Add files using upload-large-folder tool
Browse files- local-test-commons-compress-delta-03/afc-commons-compress/src/test/resources/COMPRESS-320/recreate.sh +9 -0
- local-test-commons-compress-delta-03/afc-commons-compress/src/test/resources/META-INF/services/org.apache.commons.compress.archivers.ArchiveStreamProvider +1 -0
- local-test-commons-compress-delta-03/afc-commons-compress/src/test/resources/archives/FreeBSD.ar +29 -0
- local-test-commons-compress-delta-03/afc-commons-compress/src/test/resources/archives/FreeBSD_newc.cpio +0 -0
- local-test-commons-compress-delta-03/afc-commons-compress/src/test/resources/archives/SunOS.ar +29 -0
- local-test-commons-compress-delta-03/afc-commons-compress/src/test/resources/archives/SunOS_-c.cpio +0 -0
- local-test-commons-compress-delta-03/afc-commons-compress/src/test/resources/archives/SunOS_.cpio +0 -0
- local-test-commons-compress-delta-03/afc-commons-compress/src/test/resources/longsymlink/files.txt +1 -0
- local-test-commons-compress-delta-03/afc-commons-compress/src/test/resources/org/apache/commons/compress/COMPRESS-626/compress-626-pack200.jar +0 -0
- local-test-commons-compress-delta-03/afc-commons-compress/src/test/resources/org/apache/commons/compress/ico/readme.md +18 -0
- local-test-commons-compress-delta-03/fuzz-tooling/docs/_sass/color_schemes/wider.scss +2 -0
- local-test-commons-compress-delta-03/fuzz-tooling/docs/advanced-topics/advanced_topics.md +9 -0
- local-test-commons-compress-delta-03/fuzz-tooling/docs/advanced-topics/corpora.md +70 -0
- local-test-commons-compress-delta-03/fuzz-tooling/docs/advanced-topics/fuzz_introspector.md +118 -0
- local-test-commons-compress-delta-03/fuzz-tooling/docs/further-reading/clusterfuzz.md +67 -0
- local-test-commons-compress-delta-03/fuzz-tooling/docs/further-reading/further_reading.md +9 -0
- local-test-commons-compress-delta-03/fuzz-tooling/docs/further-reading/fuzzer_environment.md +77 -0
- local-test-commons-compress-delta-03/fuzz-tooling/docs/getting-started/continuous_integration.md +271 -0
- local-test-commons-compress-delta-03/fuzz-tooling/docs/reference/glossary.md +99 -0
- local-test-commons-compress-delta-03/fuzz-tooling/docs/reference/useful_links.md +51 -0
local-test-commons-compress-delta-03/afc-commons-compress/src/test/resources/COMPRESS-320/recreate.sh
ADDED
|
@@ -0,0 +1,9 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
#!/bin/bash
|
| 2 |
+
|
| 3 |
+
rm *.7z
|
| 4 |
+
for COMPRESSION in "LZMA" "LZMA2" "PPMd" "BZip2" "Deflate" "Copy"; do
|
| 5 |
+
# New solid block every 10 files.
|
| 6 |
+
7za a -m0=$COMPRESSION -ms10f $COMPRESSION-solid.7z ../../../../src/main/java/org/apache/commons/compress/compressors
|
| 7 |
+
# Each file in isolation
|
| 8 |
+
7za a -m0=$COMPRESSION -ms=off $COMPRESSION.7z ../../../../src/main/java/org/apache/commons/compress/compressors
|
| 9 |
+
done
|
local-test-commons-compress-delta-03/afc-commons-compress/src/test/resources/META-INF/services/org.apache.commons.compress.archivers.ArchiveStreamProvider
ADDED
|
@@ -0,0 +1 @@
|
|
|
|
|
|
|
| 1 |
+
org.apache.commons.compress.archivers.TestArchiveStreamProvider
|
local-test-commons-compress-delta-03/afc-commons-compress/src/test/resources/archives/FreeBSD.ar
ADDED
|
@@ -0,0 +1,29 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
!<arch>
|
| 2 |
+
1/ 1238278221 1721 1721 100664 27 `
|
| 3 |
+
abcdefghijklmnopqrstuvwxyz
|
| 4 |
+
|
| 5 |
+
12/ 1238278221 1721 1721 100664 27 `
|
| 6 |
+
abcdefghijklmnopqrstuvwxyz
|
| 7 |
+
|
| 8 |
+
123/ 1238278221 1721 1721 100664 27 `
|
| 9 |
+
abcdefghijklmnopqrstuvwxyz
|
| 10 |
+
|
| 11 |
+
1234/ 1238278222 1721 1721 100664 27 `
|
| 12 |
+
abcdefghijklmnopqrstuvwxyz
|
| 13 |
+
|
| 14 |
+
12345/ 1238278222 1721 1721 100664 27 `
|
| 15 |
+
abcdefghijklmnopqrstuvwxyz
|
| 16 |
+
|
| 17 |
+
123450/ 1238278222 1721 1721 100644 27 `
|
| 18 |
+
abcdefghijklmnopqrstuvwxyz
|
| 19 |
+
|
| 20 |
+
123456/ 1238278222 1721 1721 100664 26 `
|
| 21 |
+
bcdefghijklmnopqrstuvwxyz
|
| 22 |
+
123457/ 1238278222 1721 1721 100644 25 `
|
| 23 |
+
cdefghijklmnopqrstuvwxyz
|
| 24 |
+
|
| 25 |
+
123458/ 1238278222 1721 1721 100644 24 `
|
| 26 |
+
defghijklmnopqrstuvwxyz
|
| 27 |
+
123459/ 1238278222 1721 1721 100644 23 `
|
| 28 |
+
efghijklmnopqrstuvwxyz
|
| 29 |
+
|
local-test-commons-compress-delta-03/afc-commons-compress/src/test/resources/archives/FreeBSD_newc.cpio
ADDED
|
Binary file (2.05 kB). View file
|
|
|
local-test-commons-compress-delta-03/afc-commons-compress/src/test/resources/archives/SunOS.ar
ADDED
|
@@ -0,0 +1,29 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
!<arch>
|
| 2 |
+
1/ 1238264462 2606 1 100644 27 `
|
| 3 |
+
abcdefghijklmnopqrstuvwxyz
|
| 4 |
+
|
| 5 |
+
12/ 1238277260 2606 1 100644 27 `
|
| 6 |
+
abcdefghijklmnopqrstuvwxyz
|
| 7 |
+
|
| 8 |
+
123/ 1238277265 2606 1 100644 27 `
|
| 9 |
+
abcdefghijklmnopqrstuvwxyz
|
| 10 |
+
|
| 11 |
+
1234/ 1238277275 2606 1 100644 27 `
|
| 12 |
+
abcdefghijklmnopqrstuvwxyz
|
| 13 |
+
|
| 14 |
+
12345/ 1238277277 2606 1 100644 27 `
|
| 15 |
+
abcdefghijklmnopqrstuvwxyz
|
| 16 |
+
|
| 17 |
+
123450/ 1238277385 2606 1 100644 27 `
|
| 18 |
+
abcdefghijklmnopqrstuvwxyz
|
| 19 |
+
|
| 20 |
+
123456/ 1238277620 2606 1 100644 26 `
|
| 21 |
+
bcdefghijklmnopqrstuvwxyz
|
| 22 |
+
123457/ 1238277660 2606 1 100644 25 `
|
| 23 |
+
cdefghijklmnopqrstuvwxyz
|
| 24 |
+
|
| 25 |
+
123458/ 1238277670 2606 1 100644 24 `
|
| 26 |
+
defghijklmnopqrstuvwxyz
|
| 27 |
+
123459/ 1238277679 2606 1 100644 23 `
|
| 28 |
+
efghijklmnopqrstuvwxyz
|
| 29 |
+
|
local-test-commons-compress-delta-03/afc-commons-compress/src/test/resources/archives/SunOS_-c.cpio
ADDED
|
Binary file (2.05 kB). View file
|
|
|
local-test-commons-compress-delta-03/afc-commons-compress/src/test/resources/archives/SunOS_.cpio
ADDED
|
Binary file (1.02 kB). View file
|
|
|
local-test-commons-compress-delta-03/afc-commons-compress/src/test/resources/longsymlink/files.txt
ADDED
|
@@ -0,0 +1 @@
|
|
|
|
|
|
|
| 1 |
+
0xxxxxxxxx10xxxxxxxx20xxxxxxxx30xxxxxxxx40xxxxxxxx50xxxxxxxx60xxxxxxxx70xxxxxxxx80xxxxxxxx90xxxxxxxx100xxxxxxx110xxxxxxx120xxxxxxx130xxxxxxx -> 0yyyyyyyyy10yyyyyyyy20yyyyyyyy30yyyyyyyy40yyyyyyyy50yyyyyyyy60yyyyyyyy70yyyyyyyy80yyyyyyyy90yyyyyyyy100yyyyyyy110yyyyyyy120yyyyyyy130yyyyyyy
|
local-test-commons-compress-delta-03/afc-commons-compress/src/test/resources/org/apache/commons/compress/COMPRESS-626/compress-626-pack200.jar
ADDED
|
Binary file (781 Bytes). View file
|
|
|
local-test-commons-compress-delta-03/afc-commons-compress/src/test/resources/org/apache/commons/compress/ico/readme.md
ADDED
|
@@ -0,0 +1,18 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
<!---
|
| 2 |
+
Licensed to the Apache Software Foundation (ASF) under one or more
|
| 3 |
+
contributor license agreements. See the NOTICE file distributed with
|
| 4 |
+
this work for additional information regarding copyright ownership.
|
| 5 |
+
The ASF licenses this file to You under the Apache License, Version 2.0
|
| 6 |
+
(the "License"); you may not use this file except in compliance with
|
| 7 |
+
the License. You may obtain a copy of the License at
|
| 8 |
+
|
| 9 |
+
http://www.apache.org/licenses/LICENSE-2.0
|
| 10 |
+
|
| 11 |
+
Unless required by applicable law or agreed to in writing, software
|
| 12 |
+
distributed under the License is distributed on an "AS IS" BASIS,
|
| 13 |
+
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
| 14 |
+
See the License for the specific language governing permissions and
|
| 15 |
+
limitations under the License.
|
| 16 |
+
-->
|
| 17 |
+
|
| 18 |
+
The ICO file in this directory are from Apache projects.
|
local-test-commons-compress-delta-03/fuzz-tooling/docs/_sass/color_schemes/wider.scss
ADDED
|
@@ -0,0 +1,2 @@
|
|
|
|
|
|
|
|
|
|
| 1 |
+
@import "./color_schemes/light";
|
| 2 |
+
$content-width: 70rem;
|
local-test-commons-compress-delta-03/fuzz-tooling/docs/advanced-topics/advanced_topics.md
ADDED
|
@@ -0,0 +1,9 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Advanced topics
|
| 4 |
+
has_children: true
|
| 5 |
+
nav_order: 3
|
| 6 |
+
permalink: /advanced-topics/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Advanced topics
|
local-test-commons-compress-delta-03/fuzz-tooling/docs/advanced-topics/corpora.md
ADDED
|
@@ -0,0 +1,70 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Corpora
|
| 4 |
+
parent: Advanced topics
|
| 5 |
+
nav_order: 3
|
| 6 |
+
permalink: /advanced-topics/corpora/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Accessing Corpora
|
| 10 |
+
{: .no_toc}
|
| 11 |
+
|
| 12 |
+
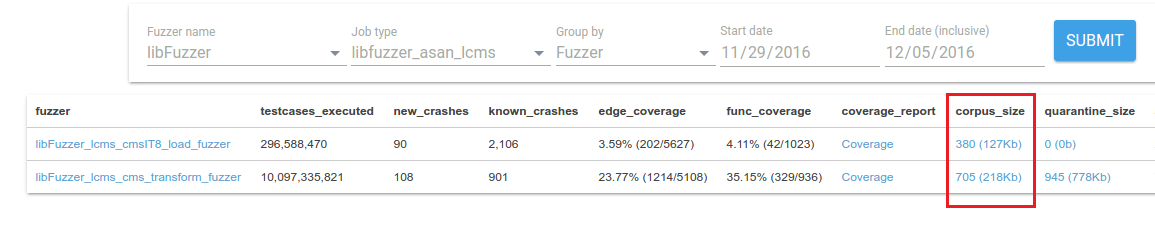
If you want to access the corpora that we are using for your fuzz targets
|
| 13 |
+
(synthesized by the fuzzing engines), follow these steps.
|
| 14 |
+
|
| 15 |
+
- TOC
|
| 16 |
+
{:toc}
|
| 17 |
+
---
|
| 18 |
+
|
| 19 |
+
## Obtain access
|
| 20 |
+
|
| 21 |
+
To get access to a project's corpora, you must be listed as the
|
| 22 |
+
primary contact or as an auto cc in the project's `project.yaml` file, as described
|
| 23 |
+
in the [New Project Guide]({{ site.baseurl }}/getting-started/new-project-guide/#projectyaml).
|
| 24 |
+
If you don't do this, most of the links below won't work.
|
| 25 |
+
|
| 26 |
+
## Install Google Cloud SDK
|
| 27 |
+
|
| 28 |
+
The corpora for fuzz targets are stored on [Google Cloud
|
| 29 |
+
Storage](https://cloud.google.com/storage/). To access them, you need to
|
| 30 |
+
[install the gsutil
|
| 31 |
+
tool](https://cloud.google.com/storage/docs/gsutil_install), which is part of
|
| 32 |
+
the Google Cloud SDK. Follow the instructions on the installation page to
|
| 33 |
+
login with the Google account listed in your project's `project.yaml` file.
|
| 34 |
+
|
| 35 |
+
## Viewing the corpus for a fuzz target
|
| 36 |
+
|
| 37 |
+
The fuzzer statistics page for your project on
|
| 38 |
+
[ClusterFuzz]({{ site.baseurl }}/further-reading/clusterfuzz)
|
| 39 |
+
contains a link to the Google Cloud console for your corpus under the
|
| 40 |
+
**corpus_size** column. Click the link to browse and download individual test inputs in the
|
| 41 |
+
corpus.
|
| 42 |
+
|
| 43 |
+
|
| 44 |
+
|
| 45 |
+
## Downloading the corpus
|
| 46 |
+
|
| 47 |
+
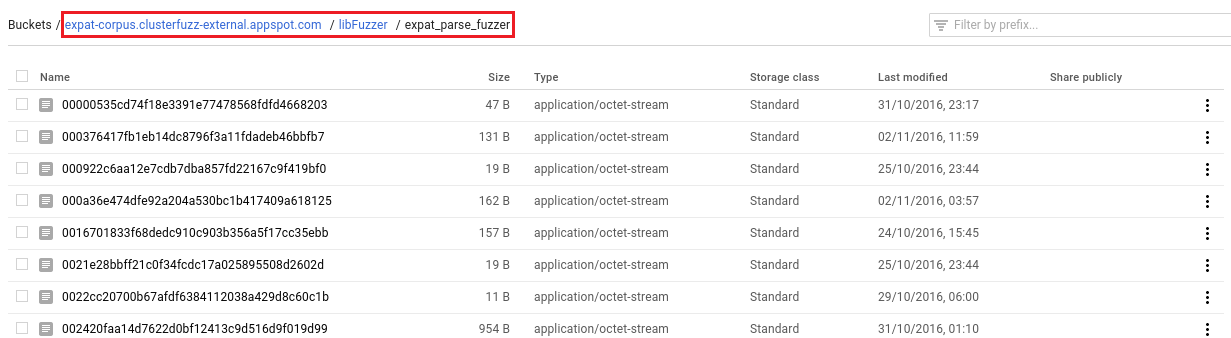
If you want to download the entire corpus, click the link in the **corpus_size** column, then
|
| 48 |
+
copy the **Buckets** path at the top of the page:
|
| 49 |
+
|
| 50 |
+
|
| 51 |
+
|
| 52 |
+
Copy the corpus to a directory on your
|
| 53 |
+
machine by running the following command:
|
| 54 |
+
|
| 55 |
+
```bash
|
| 56 |
+
$ gsutil -m cp -r gs://<bucket_path> <local_directory>
|
| 57 |
+
```
|
| 58 |
+
Using the expat example above, this would be:
|
| 59 |
+
|
| 60 |
+
```bash
|
| 61 |
+
$ gsutil -m cp -r \
|
| 62 |
+
gs://expat-corpus.clusterfuzz-external.appspot.com/libFuzzer/expat_parse_fuzzer \
|
| 63 |
+
<local_directory>
|
| 64 |
+
```
|
| 65 |
+
|
| 66 |
+
## Corpus backups
|
| 67 |
+
|
| 68 |
+
We keep daily zipped backups of your corpora. These can be accessed from the
|
| 69 |
+
**corpus_backup** column of the fuzzer statistics page. Downloading these can
|
| 70 |
+
be significantly faster than running `gsutil -m cp -r` on the corpus bucket.
|
local-test-commons-compress-delta-03/fuzz-tooling/docs/advanced-topics/fuzz_introspector.md
ADDED
|
@@ -0,0 +1,118 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Fuzz Introspector
|
| 4 |
+
parent: Advanced topics
|
| 5 |
+
nav_order: 2
|
| 6 |
+
permalink: /advanced-topics/fuzz-introspector/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Fuzz Introspector
|
| 10 |
+
{: .no_toc}
|
| 11 |
+
|
| 12 |
+
For projects written in C/C++, Python and Java you can generate Fuzz
|
| 13 |
+
Introspector reports to help guide the development of your fuzzing suite.
|
| 14 |
+
These reports help to extract details about the fuzzing setup of your
|
| 15 |
+
project with the goal of making it easier to improve the fuzzing set up.
|
| 16 |
+
The Fuzz Introspector reports are generated automatically and uploaded
|
| 17 |
+
to the cloud like code coverage reports, and you can also generate them
|
| 18 |
+
locally using the OSS-Fuzz helper script.
|
| 19 |
+
|
| 20 |
+
|
| 21 |
+
- TOC
|
| 22 |
+
{:toc}
|
| 23 |
+
---
|
| 24 |
+
|
| 25 |
+
## Fuzz Introspector overview
|
| 26 |
+
|
| 27 |
+
As soon as your project is run with ClusterFuzz (<1 day), you can view the Fuzz
|
| 28 |
+
Introspector report for your project.
|
| 29 |
+
[Fuzz Introspector](https://github.com/ossf/fuzz-introspector) helps you
|
| 30 |
+
understand your fuzzers' performance and identify any potential blockers.
|
| 31 |
+
It provides individual and aggregated fuzzer reachability and coverage reports.
|
| 32 |
+
You can monitor each fuzzer's static reachability potential and compare it
|
| 33 |
+
against dynamic coverage and identify any potential bottlenecks.
|
| 34 |
+
Fuzz Introspector can offer suggestions on increasing coverage by adding new
|
| 35 |
+
fuzz targets or modify existing ones.
|
| 36 |
+
Fuzz Introspector reports can be viewed from the [OSS-Fuzz
|
| 37 |
+
homepage](https://oss-fuzz.com/) or through this
|
| 38 |
+
[index](http://oss-fuzz-introspector.storage.googleapis.com/index.html).
|
| 39 |
+
|
| 40 |
+
- [Fuzz Introspector documentation](https://fuzz-introspector.readthedocs.io/en/latest/)
|
| 41 |
+
- [Fuzz Introspector source code](https://github.com/ossf/fuzz-introspector)
|
| 42 |
+
- [OSS-Fuzz Fuzz Introspector reports](http://oss-fuzz-introspector.storage.googleapis.com/index.html)
|
| 43 |
+
|
| 44 |
+
|
| 45 |
+
## Tutorials and guides
|
| 46 |
+
|
| 47 |
+
The reports generated can be a lot to digest when first viewing them. The
|
| 48 |
+
[Fuzz Introspector documentation](https://fuzz-introspector.readthedocs.io/en/latest/)
|
| 49 |
+
provides various user guides and tutorials rooted in OSS-Fuzz projects, which is
|
| 50 |
+
a useful reference on how to make use of the reports.
|
| 51 |
+
|
| 52 |
+
For ideas on how to use Fuzz Introspector, see [user guides](https://fuzz-introspector.readthedocs.io/en/latest/user-guides/index.html) which includes sections e.g.
|
| 53 |
+
- [Quickly extract overview of a given project](https://fuzz-introspector.readthedocs.io/en/latest/user-guides/quick-overview.html)
|
| 54 |
+
- [Get ideas for new fuzz targets](https://fuzz-introspector.readthedocs.io/en/latest/user-guides/get-ideas-for-new-targets.html)
|
| 55 |
+
- [Comparing introspector reports](https://fuzz-introspector.readthedocs.io/en/latest/user-guides/comparing-introspector-reports.html)
|
| 56 |
+
|
| 57 |
+
## Run Fuzz Introspector locally
|
| 58 |
+
|
| 59 |
+
To generate a Fuzz Introspector report locally use `infra/helper.py` and the
|
| 60 |
+
`introspector` command. Fuzz Introspector relies on code coverage to
|
| 61 |
+
analyze a given project, and this means we need to extract code coverage in the
|
| 62 |
+
Fuzz Introspector process. We can do this in two ways. First, by running the fuzzers
|
| 63 |
+
for a given amount of time, and, second, by generating code coverage using the public
|
| 64 |
+
corpus available from OSS-Fuzz.
|
| 65 |
+
|
| 66 |
+
|
| 67 |
+
### Generate reports by running fuzzers for X seconds
|
| 68 |
+
|
| 69 |
+
The following command will generate a Fuzz Introspector report for the `libdwarf` project
|
| 70 |
+
and will extract code coverage based on a corpus created from running the fuzzers for 30
|
| 71 |
+
seconds.
|
| 72 |
+
|
| 73 |
+
```bash
|
| 74 |
+
$ python3 infra/helper.py introspector libdwarf --seconds=30
|
| 75 |
+
```
|
| 76 |
+
|
| 77 |
+
If the above command was succesful, you should see output along the lines of:
|
| 78 |
+
|
| 79 |
+
```bash
|
| 80 |
+
INFO:root:To browse the report, run: python3 -m http.server 8008 --directory /home/my_user/oss-fuzz/build/out/libdwarf/introspector-report/inspector and navigate to localhost:8008/fuzz_report.html in your browser
|
| 81 |
+
```
|
| 82 |
+
The above output gives you directions on how to start a simple webserver using
|
| 83 |
+
`python3 -m http.server`, which you can use to view the Fuzz Introspector report.
|
| 84 |
+
|
| 85 |
+
### Generate reports by using public corpora
|
| 86 |
+
|
| 87 |
+
The following command will generate a Fuzz Introspector report for the `libdwarf` project
|
| 88 |
+
and will extract code coverage based on the publicly available corpora.
|
| 89 |
+
|
| 90 |
+
```bash
|
| 91 |
+
$ python3 infra/helper.py introspector libdwarf --public-corpora
|
| 92 |
+
```
|
| 93 |
+
|
| 94 |
+
Assuming the above command is succesful you can view the report using `python3 -m http.server`
|
| 95 |
+
following the example described above.
|
| 96 |
+
|
| 97 |
+
|
| 98 |
+
## Differences in build tooling
|
| 99 |
+
|
| 100 |
+
There are some differences in build environment for Fuzz Introspector builds
|
| 101 |
+
in comparison to e.g. ASAN or code coverage builds. The reason is that
|
| 102 |
+
Fuzz Introspector relies on certain compile-time tools to do its analysis.
|
| 103 |
+
This compile time tooling differs between languages, namely:
|
| 104 |
+
- For C/C++, Fuzz Introspector relies on [LLVM LTO](https://llvm.org/docs/LinkTimeOptimization.html) and [LLVM Gold](https://llvm.org/docs/GoldPlugin.html)
|
| 105 |
+
- For Python, Fuzz Introspector relies on a modified [PyCG](https://github.com/vitsalis/PyCG)
|
| 106 |
+
- For Java, Fuzz Introspector relies on [Soot](https://soot-oss.github.io/soot/)
|
| 107 |
+
|
| 108 |
+
The consequence of this is your project must be compatible with these projects.
|
| 109 |
+
PyCG and Soot have not shown to be a blocker for many projects, however, experience
|
| 110 |
+
has shown that sometimes a project's build needs modification in order to compile
|
| 111 |
+
with LLVM LTO. The easiest way to test if your project works with LLVM is checking
|
| 112 |
+
whether your project can compile with the flags `-flto -fuse-ld=gold` and using
|
| 113 |
+
the gold linker. OSS-Fuzz automatically sets these flags and linker options when
|
| 114 |
+
using `infra/helper.py` to build your project with `--sanitizer=introspector`, e.g.
|
| 115 |
+
|
| 116 |
+
```bash
|
| 117 |
+
python3 infra/helper.py build_fuzzers --sanitizer=introspector PROJ_NAME
|
| 118 |
+
```
|
local-test-commons-compress-delta-03/fuzz-tooling/docs/further-reading/clusterfuzz.md
ADDED
|
@@ -0,0 +1,67 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: ClusterFuzz
|
| 4 |
+
parent: Further reading
|
| 5 |
+
nav_order: 1
|
| 6 |
+
permalink: /further-reading/clusterfuzz/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# ClusterFuzz
|
| 10 |
+
|
| 11 |
+
[ClusterFuzz](https://github.com/google/clusterfuzz) is the distributed fuzzing
|
| 12 |
+
infrastructure behind OSS-Fuzz. It was initially built for fuzzing Chrome at
|
| 13 |
+
scale.
|
| 14 |
+
|
| 15 |
+
- TOC
|
| 16 |
+
{:toc}
|
| 17 |
+
---
|
| 18 |
+
|
| 19 |
+
## Web interface
|
| 20 |
+
|
| 21 |
+
ClusterFuzz provides a [web interface](https://oss-fuzz.com)
|
| 22 |
+
to view statistics about your fuzz targets, as well as current crashes.
|
| 23 |
+
|
| 24 |
+
*Note*: Access is restricted to project developers who we auto CC on new bug
|
| 25 |
+
reports.
|
| 26 |
+
|
| 27 |
+
## Testcase reports
|
| 28 |
+
|
| 29 |
+
ClusterFuzz will automatically de-duplicate and file reproducible crashes into
|
| 30 |
+
our [bug tracker](https://bugs.chromium.org/p/oss-fuzz/issues/list). We provide
|
| 31 |
+
a crash report page that gives you the stack trace, a link to the crashing
|
| 32 |
+
testcase, and regression ranges where the bug was most likely introduced.
|
| 33 |
+
|
| 34 |
+

|
| 35 |
+
|
| 36 |
+
## Fuzzer stats
|
| 37 |
+
|
| 38 |
+
You can view statistics about your fuzz targets (e.g. speed, coverage
|
| 39 |
+
information, memory usage) on our fuzzer statistics dashboard.
|
| 40 |
+
|
| 41 |
+

|
| 42 |
+
|
| 43 |
+

|
| 44 |
+
|
| 45 |
+
## Coverage reports
|
| 46 |
+
|
| 47 |
+
We provide coverage reports, where we highlight the parts of source code that
|
| 48 |
+
are being reached by your fuzz target. Make sure to look at the uncovered code
|
| 49 |
+
marked in red and add appropriate fuzz targets to cover those use cases.
|
| 50 |
+
|
| 51 |
+

|
| 52 |
+

|
| 53 |
+
|
| 54 |
+
## Performance analyzer
|
| 55 |
+
|
| 56 |
+
You can view performance issues that your fuzz target is running into (e.g.
|
| 57 |
+
leaks, timeouts, etc) by clicking on `Performance` link on our fuzzer statistics
|
| 58 |
+
dashboard. Make sure to fix all cited issues, so as to keep your fuzz target
|
| 59 |
+
running efficiently and finding new bugs.
|
| 60 |
+
|
| 61 |
+

|
| 62 |
+
|
| 63 |
+
## Crash stats
|
| 64 |
+
|
| 65 |
+
You can view statistics of crashes over time on our crash statistics dashboard.
|
| 66 |
+
|
| 67 |
+

|
local-test-commons-compress-delta-03/fuzz-tooling/docs/further-reading/further_reading.md
ADDED
|
@@ -0,0 +1,9 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Further reading
|
| 4 |
+
has_children: true
|
| 5 |
+
nav_order: 4
|
| 6 |
+
permalink: /further-reading/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Further reading
|
local-test-commons-compress-delta-03/fuzz-tooling/docs/further-reading/fuzzer_environment.md
ADDED
|
@@ -0,0 +1,77 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Fuzzer environment
|
| 4 |
+
parent: Further reading
|
| 5 |
+
nav_order: 2
|
| 6 |
+
permalink: /further-reading/fuzzer-environment/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Fuzzer environment on ClusterFuzz
|
| 10 |
+
|
| 11 |
+
Your fuzz targets will be run on a
|
| 12 |
+
[Google Compute Engine](https://cloud.google.com/compute/) VM (Linux).
|
| 13 |
+
|
| 14 |
+
- TOC
|
| 15 |
+
{:toc}
|
| 16 |
+
---
|
| 17 |
+
|
| 18 |
+
## Runtime Dependencies
|
| 19 |
+
|
| 20 |
+
You should not make any assumptions on the availability of dependent packages
|
| 21 |
+
in the execution environment. Packages that are installed via
|
| 22 |
+
[Dockerfile]({{ site.baseurl }}/getting-started/new-project-guide/#dockerfile)
|
| 23 |
+
or built as part of
|
| 24 |
+
[build.sh]({{ site.baseurl }}/getting-started/new-project-guide/#buildsh)
|
| 25 |
+
are not available on the bot runtime environment (where the fuzz targets run).
|
| 26 |
+
|
| 27 |
+
If you need these dependencies in the runtime environment, you can either:
|
| 28 |
+
- Install the packages via Dockerfile
|
| 29 |
+
([example](https://github.com/google/oss-fuzz/blob/2d5e2ef84f281e6ab789055aa735606d3122fda9/projects/tor/Dockerfile#L19))
|
| 30 |
+
and then link statically against them
|
| 31 |
+
([example](https://github.com/google/oss-fuzz/blob/2d5e2ef84f281e6ab789055aa735606d3122fda9/projects/tor/build.sh#L40)).
|
| 32 |
+
- Or build the dependencies statically in
|
| 33 |
+
[build.sh]({{ site.baseurl }}/getting-started/new-project-guide/#buildsh)
|
| 34 |
+
([example](https://github.com/google/oss-fuzz/blob/64f8b6593da141b97c98c7bc6f07df92c42ee010/projects/ffmpeg/build.sh#L26)).
|
| 35 |
+
|
| 36 |
+
All build artifacts needed during fuzz target execution should be inside the
|
| 37 |
+
`$OUT` directory. Only those artifacts are archived and used on the bots.
|
| 38 |
+
Everything else is ignored (e.g. artifacts in `$WORK`, `$SRC`, etc) and hence
|
| 39 |
+
is not available in the execution environment.
|
| 40 |
+
|
| 41 |
+
We strongly recommend static linking because it just works.
|
| 42 |
+
However dynamic linking can work if shared objects are included in the `$OUT` directory and are loaded relative
|
| 43 |
+
to `'$ORIGIN'`, the path of the binary (see the discussion of `'$ORIGIN'` [here](http://man7.org/linux/man-pages/man8/ld.so.8.html)).
|
| 44 |
+
A fuzzer can be instructed to load libraries relative to `'$ORIGIN'` during compilation (i.e. `-Wl,-rpath,'$ORIGIN/lib'` )
|
| 45 |
+
or afterwards using `chrpath -r '$ORIGIN/lib' $OUT/$fuzzerName` ([example](https://github.com/google/oss-fuzz/blob/09aa9ac556f97bd4e31928747eca0c8fed42509f/projects/php/build.sh#L40)). Note that `'$ORIGIN'` should be surrounded
|
| 46 |
+
by single quotes because it is not an environment variable like `$OUT` that can be retrieved during execution of `build.sh`.
|
| 47 |
+
Its value is retrieved during execution of the binary. You can verify that you did this correctly using `ldd <fuzz_target_name>` and the `check_build` command in `infra/helper.py`.
|
| 48 |
+
|
| 49 |
+
You should ensure that the fuzz target works correctly by using `run_fuzzer`
|
| 50 |
+
command (see instructions
|
| 51 |
+
[here]({{ site.baseurl }}/getting-started/new-project-guide/#testing-locally)).
|
| 52 |
+
This command uses a clean base-runner docker container and not the base-builder
|
| 53 |
+
docker container created during build-time.
|
| 54 |
+
|
| 55 |
+
## argv[0]
|
| 56 |
+
|
| 57 |
+
You must not modify `argv[0]`. It is required for certain things to work
|
| 58 |
+
correctly.
|
| 59 |
+
|
| 60 |
+
## Current working directory
|
| 61 |
+
|
| 62 |
+
You should not make any assumptions about the current working directory of your
|
| 63 |
+
fuzz target. If you need to load data files, please use `argv[0]` to get the
|
| 64 |
+
directory where your fuzz target executable is located.
|
| 65 |
+
|
| 66 |
+
## File system
|
| 67 |
+
|
| 68 |
+
Everything except `/tmp` is read-only, including the directory that your fuzz
|
| 69 |
+
target executable lives in.
|
| 70 |
+
|
| 71 |
+
`/dev` is also unavailable.
|
| 72 |
+
|
| 73 |
+
## Hardware
|
| 74 |
+
|
| 75 |
+
Your project should not be compiled with `-march=native` or `-mtune=native`
|
| 76 |
+
flags, as the build infrastructure and fuzzing machines may have different CPUs
|
| 77 |
+
as well as other hardware differences. You may however use `-mtune=generic`.
|
local-test-commons-compress-delta-03/fuzz-tooling/docs/getting-started/continuous_integration.md
ADDED
|
@@ -0,0 +1,271 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Continuous Integration
|
| 4 |
+
parent: Getting started
|
| 5 |
+
nav_order: 5
|
| 6 |
+
permalink: /getting-started/continuous-integration/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Continuous Integration
|
| 10 |
+
|
| 11 |
+
OSS-Fuzz offers **CIFuzz**, a GitHub action/CI job that runs your fuzz targets
|
| 12 |
+
on pull requests. This works similarly to running unit tests in CI. CIFuzz helps
|
| 13 |
+
you find and fix bugs before they make it into your codebase.
|
| 14 |
+
Currently, CIFuzz primarily supports projects hosted on GitHub.
|
| 15 |
+
Non-OSS-Fuzz users can use CIFuzz with additional features through
|
| 16 |
+
[ClusterFuzzLite](https://google.github.io/clusterfuzzlite/).
|
| 17 |
+
|
| 18 |
+
## How it works
|
| 19 |
+
|
| 20 |
+
CIFuzz builds your project's fuzzers from the source at a particular
|
| 21 |
+
pull request or commit. Then CIFuzz runs the fuzzers for a short amount of time.
|
| 22 |
+
If CIFuzz finds a crash, CIFuzz reports the stacktrace, makes the crashing
|
| 23 |
+
input available for download and the CI test fails (red X).
|
| 24 |
+
|
| 25 |
+
If CIFuzz doesn't find a crash during the allotted time, the CI test passes
|
| 26 |
+
(green check). If CIFuzz finds a crash, it reports the crash only if both of
|
| 27 |
+
following are true:
|
| 28 |
+
* The crash is reproducible (on the PR/commit build).
|
| 29 |
+
* The crash does not occur on older OSS-Fuzz builds. (If the crash does occur
|
| 30 |
+
on older builds, then it was not introduced by the PR/commit
|
| 31 |
+
being tested.)
|
| 32 |
+
|
| 33 |
+
If your project supports [OSS-Fuzz's code coverage]({{ site.baseurl }}/advanced-topics/code-coverage),
|
| 34 |
+
CIFuzz only runs the fuzzers affected by a pull request/commit.
|
| 35 |
+
Otherwise it will divide up the allotted fuzzing time (10 minutes by default)
|
| 36 |
+
among all fuzzers in the project.
|
| 37 |
+
|
| 38 |
+
CIFuzz uses 30 day old/public regressions and corpora from OSS-Fuzz. This makes
|
| 39 |
+
fuzzing more effective and gives you regression testing for free.
|
| 40 |
+
|
| 41 |
+
## Requirements
|
| 42 |
+
|
| 43 |
+
1. Your project must be integrated with OSS-Fuzz.
|
| 44 |
+
1. Your project is hosted on GitHub.
|
| 45 |
+
1. Your repository needs to be cloned with `git` in oss-fuzz Dockerfile (do not use `go get` or other methods)
|
| 46 |
+
|
| 47 |
+
## Integrating into your repository
|
| 48 |
+
|
| 49 |
+
You can integrate CIFuzz into your project using the following steps:
|
| 50 |
+
1. Create a `.github` directory in the root of your project.
|
| 51 |
+
1. Create a `workflows` directory inside of your `.github` directory.
|
| 52 |
+
1. Copy the example [`cifuzz.yml`](https://github.com/google/oss-fuzz/blob/master/infra/cifuzz/example_cifuzz.yml)
|
| 53 |
+
file over from the OSS-Fuzz repository to the `workflows` directory.
|
| 54 |
+
1. Change the `oss-fuzz-project-name` value in `cifuzz.yml` from `example` to the name of your OSS-Fuzz project. It is **very important** that you use your OSS-Fuzz project name which is case sensitive. This name
|
| 55 |
+
is the name of your project's subdirectory in the [`projects`](https://github.com/google/oss-fuzz/tree/master/projects) directory of OSS-Fuzz.
|
| 56 |
+
1. Set the value of `fuzz-seconds`. The longest time that the project maintainers are acceptable with should be used. This value should be at minimum 600 seconds and scale with project size.
|
| 57 |
+
|
| 58 |
+
Your directory structure should look like the following:
|
| 59 |
+
```
|
| 60 |
+
project
|
| 61 |
+
|___ .github
|
| 62 |
+
| |____ workflows
|
| 63 |
+
| |____ cifuzz.yml
|
| 64 |
+
|___ other-files
|
| 65 |
+
```
|
| 66 |
+
|
| 67 |
+
cifuzz.yml for an example project:
|
| 68 |
+
|
| 69 |
+
```yaml
|
| 70 |
+
name: CIFuzz
|
| 71 |
+
on: [pull_request]
|
| 72 |
+
permissions: {}
|
| 73 |
+
jobs:
|
| 74 |
+
Fuzzing:
|
| 75 |
+
runs-on: ubuntu-latest
|
| 76 |
+
permissions:
|
| 77 |
+
security-events: write
|
| 78 |
+
steps:
|
| 79 |
+
- name: Build Fuzzers
|
| 80 |
+
id: build
|
| 81 |
+
uses: google/oss-fuzz/infra/cifuzz/actions/build_fuzzers@master
|
| 82 |
+
with:
|
| 83 |
+
oss-fuzz-project-name: 'example'
|
| 84 |
+
language: c++
|
| 85 |
+
- name: Run Fuzzers
|
| 86 |
+
uses: google/oss-fuzz/infra/cifuzz/actions/run_fuzzers@master
|
| 87 |
+
with:
|
| 88 |
+
oss-fuzz-project-name: 'example'
|
| 89 |
+
language: c++
|
| 90 |
+
fuzz-seconds: 600
|
| 91 |
+
output-sarif: true
|
| 92 |
+
- name: Upload Crash
|
| 93 |
+
uses: actions/upload-artifact@v3
|
| 94 |
+
if: failure() && steps.build.outcome == 'success'
|
| 95 |
+
with:
|
| 96 |
+
name: artifacts
|
| 97 |
+
path: ./out/artifacts
|
| 98 |
+
- name: Upload Sarif
|
| 99 |
+
if: always() && steps.build.outcome == 'success'
|
| 100 |
+
uses: github/codeql-action/upload-sarif@v2
|
| 101 |
+
with:
|
| 102 |
+
# Path to SARIF file relative to the root of the repository
|
| 103 |
+
sarif_file: cifuzz-sarif/results.sarif
|
| 104 |
+
checkout_path: cifuzz-sarif
|
| 105 |
+
```
|
| 106 |
+
|
| 107 |
+
|
| 108 |
+
### Optional configuration
|
| 109 |
+
|
| 110 |
+
#### Configurable Variables
|
| 111 |
+
|
| 112 |
+
`language`: (optional) The language your target program is written in. Defaults
|
| 113 |
+
to `c++`. This should be the same as the value you set in `project.yaml`. See
|
| 114 |
+
[this explanation]({{ site.baseurl }}//getting-started/new-project-guide/#language)
|
| 115 |
+
for more details.
|
| 116 |
+
|
| 117 |
+
`fuzz-seconds`: Determines how long CIFuzz spends fuzzing your project in seconds.
|
| 118 |
+
The default is 600 seconds. The GitHub Actions max run time is 21600 seconds (6
|
| 119 |
+
hours). This variable is only meaningful when supplied to the `run_fuzzers`
|
| 120 |
+
action, not the `build_fuzzers` action.
|
| 121 |
+
|
| 122 |
+
`dry-run`: Determines if CIFuzz surfaces errors. The default value is `false`. When set to `true`,
|
| 123 |
+
CIFuzz will never report a failure even if it finds a crash in your project.
|
| 124 |
+
This requires the user to manually check the logs for detected bugs. If dry run mode is desired,
|
| 125 |
+
make sure to set the dry-run parameters in both the `Build Fuzzers` and `Run Fuzzers` action step.
|
| 126 |
+
|
| 127 |
+
`allowed-broken-targets-percentage`: Can be set if you want to set a stricter
|
| 128 |
+
limit for broken fuzz targets than OSS-Fuzz's check_build. Most users should
|
| 129 |
+
not set this. This value is only meaningful when supplied to the `run_fuzzers`
|
| 130 |
+
action, not the `build_fuzzers` action.
|
| 131 |
+
|
| 132 |
+
`sanitizer`: Determines a sanitizer to build and run fuzz targets with. The choices are `'address'`,
|
| 133 |
+
`'memory'` and `'undefined'`. The default is `'address'`. It is important to note that the `Build Fuzzers`
|
| 134 |
+
and the `Run Fuzzers` sanitizer field needs to be the same. To specify a list of sanitizers
|
| 135 |
+
a [matrix](https://help.github.com/en/actions/reference/workflow-syntax-for-github-actions#jobsjob_idstrategymatrix)
|
| 136 |
+
can be used. To use a sanitizer add it to the list of sanitizers in the matrix field below:
|
| 137 |
+
|
| 138 |
+
`report-timeouts`: Determines whether to report fails due to timeouts.
|
| 139 |
+
|
| 140 |
+
`report-ooms`: Determines whether to report fails due to OOM.
|
| 141 |
+
|
| 142 |
+
```yaml
|
| 143 |
+
{% raw %}
|
| 144 |
+
name: CIFuzz
|
| 145 |
+
on: [pull_request]
|
| 146 |
+
permissions: {}
|
| 147 |
+
jobs:
|
| 148 |
+
Fuzzing:
|
| 149 |
+
runs-on: ubuntu-latest
|
| 150 |
+
permissions:
|
| 151 |
+
security-events: write
|
| 152 |
+
strategy:
|
| 153 |
+
fail-fast: false
|
| 154 |
+
matrix:
|
| 155 |
+
sanitizer: [address, undefined, memory]
|
| 156 |
+
steps:
|
| 157 |
+
- name: Build Fuzzers (${{ matrix.sanitizer }})
|
| 158 |
+
id: build
|
| 159 |
+
uses: google/oss-fuzz/infra/cifuzz/actions/build_fuzzers@master
|
| 160 |
+
with:
|
| 161 |
+
oss-fuzz-project-name: 'example'
|
| 162 |
+
language: c++
|
| 163 |
+
sanitizer: ${{ matrix.sanitizer }}
|
| 164 |
+
- name: Run Fuzzers (${{ matrix.sanitizer }})
|
| 165 |
+
uses: google/oss-fuzz/infra/cifuzz/actions/run_fuzzers@master
|
| 166 |
+
with:
|
| 167 |
+
oss-fuzz-project-name: 'example'
|
| 168 |
+
language: c++
|
| 169 |
+
fuzz-seconds: 600
|
| 170 |
+
sanitizer: ${{ matrix.sanitizer }}
|
| 171 |
+
output-sarif: true
|
| 172 |
+
- name: Upload Crash
|
| 173 |
+
uses: actions/upload-artifact@v3
|
| 174 |
+
if: steps.build.outcome == 'success'
|
| 175 |
+
with:
|
| 176 |
+
name: ${{ matrix.sanitizer }}-artifacts
|
| 177 |
+
path: ./out/artifacts
|
| 178 |
+
- name: Upload Sarif
|
| 179 |
+
if: always() && steps.build.outcome == 'success'
|
| 180 |
+
uses: github/codeql-action/upload-sarif@v2
|
| 181 |
+
with:
|
| 182 |
+
# Path to SARIF file relative to the root of the repository
|
| 183 |
+
sarif_file: cifuzz-sarif/results.sarif
|
| 184 |
+
checkout_path: cifuzz-sarif
|
| 185 |
+
{% endraw %}
|
| 186 |
+
```
|
| 187 |
+
|
| 188 |
+
#### Branches and paths
|
| 189 |
+
|
| 190 |
+
You can make CIFuzz trigger only on certain branches or paths by following the
|
| 191 |
+
instructions [here](https://docs.github.com/en/actions/reference/workflow-syntax-for-github-actions).
|
| 192 |
+
For example, the following code can used to trigger CIFuzz only on changes to
|
| 193 |
+
C/C++ code residing on master and release branches:
|
| 194 |
+
|
| 195 |
+
```yaml
|
| 196 |
+
name: CIFuzz
|
| 197 |
+
on:
|
| 198 |
+
pull_request:
|
| 199 |
+
branches:
|
| 200 |
+
- master
|
| 201 |
+
- 'releases/**'
|
| 202 |
+
paths:
|
| 203 |
+
- '**.c'
|
| 204 |
+
- '**.cc'
|
| 205 |
+
- '**.cpp'
|
| 206 |
+
- '**.cxx'
|
| 207 |
+
- '**.h'
|
| 208 |
+
permissions: {}
|
| 209 |
+
jobs:
|
| 210 |
+
Fuzzing:
|
| 211 |
+
runs-on: ubuntu-latest
|
| 212 |
+
steps:
|
| 213 |
+
- name: Build Fuzzers
|
| 214 |
+
id: build
|
| 215 |
+
uses: google/oss-fuzz/infra/cifuzz/actions/build_fuzzers@master
|
| 216 |
+
with:
|
| 217 |
+
oss-fuzz-project-name: 'example'
|
| 218 |
+
language: c++
|
| 219 |
+
- name: Run Fuzzers
|
| 220 |
+
uses: google/oss-fuzz/infra/cifuzz/actions/run_fuzzers@master
|
| 221 |
+
with:
|
| 222 |
+
oss-fuzz-project-name: 'example'
|
| 223 |
+
language: c++
|
| 224 |
+
fuzz-seconds: 600
|
| 225 |
+
- name: Upload Crash
|
| 226 |
+
uses: actions/upload-artifact@v3
|
| 227 |
+
if: failure() && steps.build.outcome == 'success'
|
| 228 |
+
with:
|
| 229 |
+
name: artifacts
|
| 230 |
+
path: ./out/artifacts
|
| 231 |
+
```
|
| 232 |
+
|
| 233 |
+
You can checkout CIFuzz configs for OSS-Fuzz projects. Example -
|
| 234 |
+
[systemd](https://github.com/systemd/systemd/blob/main/.github/workflows/cifuzz.yml),
|
| 235 |
+
[curl](https://github.com/curl/curl/blob/master/.github/workflows/fuzz.yml).
|
| 236 |
+
|
| 237 |
+
## Understanding results
|
| 238 |
+
|
| 239 |
+
The results of CIFuzz can be found in two different places.
|
| 240 |
+
|
| 241 |
+
* Run fuzzers log:
|
| 242 |
+
1. This log can be accessed in the `actions` tab of a CIFuzz integrated repo.
|
| 243 |
+
1. Click on the `CIFuzz` button in the workflow selector on the left hand side.
|
| 244 |
+
1. Click on the event triggered by your desired pull request.
|
| 245 |
+
1. Click the `Fuzzing` workflow.
|
| 246 |
+
1. Select the `Run Fuzzer` drop down. It should show the timestamps and results
|
| 247 |
+
from each of the fuzz targets.
|
| 248 |
+
|
| 249 |
+

|
| 250 |
+
|
| 251 |
+
|
| 252 |
+
|
| 253 |
+
* Artifacts:
|
| 254 |
+
When the fuzzer crashes the input file that causes the crash is uploaded as an
|
| 255 |
+
artifact.
|
| 256 |
+
To download the artifact, do the following steps:
|
| 257 |
+
1. Click on the summary from the run, as illustrated in the screenshot below:
|
| 258 |
+
|
| 259 |
+
![github-actions-summary]
|
| 260 |
+
|
| 261 |
+
2. Click on the artifact you wish to download from the summary page, as
|
| 262 |
+
illustrated in the screenshot below:
|
| 263 |
+
|
| 264 |
+
![github-actions-download-crash]
|
| 265 |
+
|
| 266 |
+
[github-actions-summary]: (https://raw.githubusercontent.com/google/clusterfuzzlite/refs/heads/bucket/images/github-actions-summary.png)
|
| 267 |
+
[github-actions-download-crash]: (https://raw.githubusercontent.com/google/clusterfuzzlite/refs/heads/bucket/images/github-actions-download-crash.png)
|
| 268 |
+
|
| 269 |
+
## Feedback/Questions/Issues
|
| 270 |
+
|
| 271 |
+
Create an issue in [OSS-Fuzz](https://github.com/google/oss-fuzz/issues/new) if you have questions or any other feedback on CIFuzz.
|
local-test-commons-compress-delta-03/fuzz-tooling/docs/reference/glossary.md
ADDED
|
@@ -0,0 +1,99 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Glossary
|
| 4 |
+
nav_order: 1
|
| 5 |
+
permalink: /reference/glossary/
|
| 6 |
+
parent: Reference
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Glossary
|
| 10 |
+
|
| 11 |
+
For general fuzzing terms, see the [glossary] from [google/fuzzing] project.
|
| 12 |
+
|
| 13 |
+
[glossary]: https://github.com/google/fuzzing/blob/master/docs/glossary.md
|
| 14 |
+
[google/fuzzing]: https://github.com/google/fuzzing
|
| 15 |
+
|
| 16 |
+
- TOC
|
| 17 |
+
{:toc}
|
| 18 |
+
---
|
| 19 |
+
|
| 20 |
+
## OSS-Fuzz specific terms
|
| 21 |
+
|
| 22 |
+
### ClusterFuzz
|
| 23 |
+
|
| 24 |
+
A scalable fuzzing infrastructure that is used for OSS-Fuzz backend.
|
| 25 |
+
[ClusterFuzz] is also used to fuzz Chrome and many other projects. A quick
|
| 26 |
+
overview of ClusterFuzz user interface is available on this [page].
|
| 27 |
+
|
| 28 |
+
[page]: {{ site.baseurl }}/further-reading/clusterfuzz
|
| 29 |
+
[ClusterFuzz]: https://github.com/google/clusterfuzz
|
| 30 |
+
|
| 31 |
+
### Fuzz Target
|
| 32 |
+
|
| 33 |
+
In addition to its
|
| 34 |
+
[general definition](https://github.com/google/fuzzing/blob/master/docs/glossary.md#fuzz-target),
|
| 35 |
+
in OSS-Fuzz a fuzz target can be used to
|
| 36 |
+
[reproduce bug reports]({{ site.baseurl }}/advanced-topics/reproducing/).
|
| 37 |
+
It is recommended to use it for regression testing as well (see
|
| 38 |
+
[ideal integration]({{ site.baseurl }}/advanced-topics/ideal-integration/)).
|
| 39 |
+
|
| 40 |
+
### Job type
|
| 41 |
+
|
| 42 |
+
Or **Fuzzer Build**.
|
| 43 |
+
|
| 44 |
+
This refers to a build that contains all the [fuzz targets] for a given
|
| 45 |
+
[project](#project), is run with a specific [fuzzing engine], in a specific
|
| 46 |
+
build mode (e.g. with enabled/disabled assertions), and optionally combined
|
| 47 |
+
with a [sanitizer].
|
| 48 |
+
|
| 49 |
+
For example, we have a "libfuzzer_asan_sqlite" job type, indicating a build of
|
| 50 |
+
all sqlite3 [fuzz targets] using [libFuzzer](http://libfuzzer.info) and
|
| 51 |
+
[ASan](http://clang.llvm.org/docs/AddressSanitizer.html).
|
| 52 |
+
|
| 53 |
+
### Project
|
| 54 |
+
|
| 55 |
+
A project is an open source software project that is integrated with OSS-Fuzz.
|
| 56 |
+
Each project has a single set of configuration files
|
| 57 |
+
(example: [expat](https://github.com/google/oss-fuzz/tree/master/projects/expat))
|
| 58 |
+
and may have one or more [fuzz targets]
|
| 59 |
+
(example: [openssl](https://github.com/openssl/openssl/blob/master/fuzz/)).
|
| 60 |
+
|
| 61 |
+
### Reproducer
|
| 62 |
+
|
| 63 |
+
Or a **testcase**.
|
| 64 |
+
|
| 65 |
+
A [test input] that causes a specific bug to reproduce.
|
| 66 |
+
|
| 67 |
+
[fuzz targets]: https://github.com/google/fuzzing/blob/master/docs/glossary.md#fuzz-target
|
| 68 |
+
[fuzzing engine]: https://github.com/google/fuzzing/blob/master/docs/glossary.md#fuzzing-engine
|
| 69 |
+
[sanitizer]: https://github.com/google/fuzzing/blob/master/docs/glossary.md#sanitizer
|
| 70 |
+
[test input]: https://github.com/google/fuzzing/blob/master/docs/glossary.md#test-input
|
| 71 |
+
|
| 72 |
+
### Sanitizers
|
| 73 |
+
|
| 74 |
+
Fuzzers are usually built with one or more [sanitizer](https://github.com/google/sanitizers) enabled.
|
| 75 |
+
|
| 76 |
+
```bash
|
| 77 |
+
$ python infra/helper.py build_fuzzers --sanitizer undefined json
|
| 78 |
+
```
|
| 79 |
+
|
| 80 |
+
Supported sanitizers:
|
| 81 |
+
|
| 82 |
+
| Sanitizer | Description
|
| 83 |
+
| ------------ | ----------
|
| 84 |
+
| `address` *(default)* | [Address Sanitizer](https://github.com/google/sanitizers/wiki/AddressSanitizer) with [Leak Sanitizer](https://github.com/google/sanitizers/wiki/AddressSanitizerLeakSanitizer).
|
| 85 |
+
| `undefined` | [Undefined Behavior Sanitizer](http://clang.llvm.org/docs/UndefinedBehaviorSanitizer.html).
|
| 86 |
+
| `memory` | [Memory Sanitizer](https://github.com/google/sanitizers/wiki/MemorySanitizer).<br/>*NOTE: It is critical that you build __all__ the code in your program (including libraries it uses) with Memory Sanitizer. Otherwise, you will see false positive crashes due to an inability to see initializations in uninstrumented code.*
|
| 87 |
+
| `coverage` | Used for generating code coverage reports. See [Code Coverage doc]({{ site.baseurl }}/advanced-topics/code-coverage/).
|
| 88 |
+
|
| 89 |
+
Compiler flag values for predefined configurations are specified in the [Dockerfile](https://github.com/google/oss-fuzz/blob/master/infra/base-images/base-builder/Dockerfile).
|
| 90 |
+
These flags can be overridden by specifying `$SANITIZER_FLAGS` directly.
|
| 91 |
+
|
| 92 |
+
You can choose which configurations to automatically run your fuzzers with in `project.yaml` file (e.g. [sqlite3](https://github.com/google/oss-fuzz/tree/master/projects/sqlite3/project.yaml)).
|
| 93 |
+
|
| 94 |
+
### Architectures
|
| 95 |
+
ClusterFuzz supports fuzzing on x86_64 (aka x64) by default. However you can also fuzz using AddressSanitizer and libFuzzer on i386 (aka x86, or 32 bit) by specifying the `$ARCHITECTURE` build environment variable using the `--architecture` option:
|
| 96 |
+
|
| 97 |
+
```bash
|
| 98 |
+
python infra/helper.py build_fuzzers --architecture i386 json
|
| 99 |
+
```
|
local-test-commons-compress-delta-03/fuzz-tooling/docs/reference/useful_links.md
ADDED
|
@@ -0,0 +1,51 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Useful links
|
| 4 |
+
nav_order: 2
|
| 5 |
+
permalink: /reference/useful-links/
|
| 6 |
+
parent: Reference
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Useful links
|
| 10 |
+
|
| 11 |
+
- TOC
|
| 12 |
+
{:toc}
|
| 13 |
+
---
|
| 14 |
+
|
| 15 |
+
## Web Interface
|
| 16 |
+
|
| 17 |
+
* The main page: [oss-fuzz.com](https://oss-fuzz.com)
|
| 18 |
+
|
| 19 |
+
## Build Status
|
| 20 |
+
|
| 21 |
+
* [This page](https://oss-fuzz-build-logs.storage.googleapis.com/index.html)
|
| 22 |
+
gives the latest build logs for each project.
|
| 23 |
+
|
| 24 |
+
## Blog posts
|
| 25 |
+
|
| 26 |
+
* 2016-12-01 - Announcing OSS-Fuzz: Continuous fuzzing for open source software
|
| 27 |
+
([Open Source](https://opensource.googleblog.com/2016/12/announcing-oss-fuzz-continuous-fuzzing.html),
|
| 28 |
+
[Testing](https://testing.googleblog.com/2016/12/announcing-oss-fuzz-continuous-fuzzing.html),
|
| 29 |
+
[Security](https://security.googleblog.com/2016/12/announcing-oss-fuzz-continuous-fuzzing.html))
|
| 30 |
+
* 2017-05-08 - OSS-Fuzz: Five months later, and rewarding projects
|
| 31 |
+
([Open Source](https://opensource.googleblog.com/2017/05/oss-fuzz-five-months-later-and.html),
|
| 32 |
+
[Testing](https://testing.googleblog.com/2017/05/oss-fuzz-five-months-later-and.html),
|
| 33 |
+
[Security](https://security.googleblog.com/2017/05/oss-fuzz-five-months-later-and.html))
|
| 34 |
+
* 2018-11-06 - A New Chapter for OSS-Fuzz
|
| 35 |
+
([Security](https://security.googleblog.com/2018/11/a-new-chapter-for-oss-fuzz.html))
|
| 36 |
+
* 2020-10-09 - [Fuzzing internships for Open Source Software](https://security.googleblog.com/2020/10/fuzzing-internships-for-open-source.html)
|
| 37 |
+
* 2020-12-07 - [Improving open source security during the Google summer internship program](https://security.googleblog.com/2020/12/improving-open-source-security-during.html)
|
| 38 |
+
* 2021-03-10 - [Fuzzing Java in OSS-Fuzz](https://security.googleblog.com/2021/03/fuzzing-java-in-oss-fuzz.html)
|
| 39 |
+
* 2021-12-16 - [Improving OSS-Fuzz and Jazzer to catch Log4Shell](https://security.googleblog.com/2021/12/improving-oss-fuzz-and-jazzer-to-catch.html)
|
| 40 |
+
* 2022-09-08 - [Fuzzing beyond memory corruption: Finding broader classes of vulnerabilities automatically](https://security.googleblog.com/2022/09/fuzzing-beyond-memory-corruption.html)
|
| 41 |
+
* 2023-02-01 - [Taking the next step: OSS-Fuzz in 2023](https://security.googleblog.com/2023/02/taking-next-step-oss-fuzz-in-2023.html)
|
| 42 |
+
|
| 43 |
+
## Tutorials
|
| 44 |
+
|
| 45 |
+
* [libFuzzer documentation](https://llvm.org/docs/LibFuzzer.html)
|
| 46 |
+
* [libFuzzer tutorial](https://github.com/google/fuzzing/blob/master/tutorial/libFuzzerTutorial.md)
|
| 47 |
+
* [libFuzzer workshop](https://github.com/Dor1s/libfuzzer-workshop)
|
| 48 |
+
* [Structure-Aware Fuzzing with libFuzzer](https://github.com/google/fuzzer-test-suite/blob/master/tutorial/structure-aware-fuzzing.md)
|
| 49 |
+
* [Chromium Fuzzing Page](https://chromium.googlesource.com/chromium/src/testing/libfuzzer/)
|
| 50 |
+
* [Chromium Efficient Fuzzing Guide](https://chromium.googlesource.com/chromium/src/testing/libfuzzer/+/HEAD/efficient_fuzzing.md)
|
| 51 |
+
* [ClusterFuzz documentation](https://google.github.io/clusterfuzz/)
|