Add files using upload-large-folder tool
Browse files- local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/advanced-topics/advanced_topics.md +9 -0
- local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/advanced-topics/bug_fixing_guidance.md +94 -0
- local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/advanced-topics/code_coverage.md +130 -0
- local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/advanced-topics/corpora.md +70 -0
- local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/advanced-topics/debugging.md +45 -0
- local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/advanced-topics/fuzz_introspector.md +118 -0
- local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/advanced-topics/ideal_integration.md +174 -0
- local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/advanced-topics/reproducing.md +160 -0
- local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/assets/css/just-the-docs-wider.scss +3 -0
- local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/further-reading/clusterfuzz.md +67 -0
- local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/further-reading/further_reading.md +9 -0
- local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/further-reading/fuzzer_environment.md +77 -0
- local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/getting-started/bug_disclosure_guidelines.md +23 -0
- local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/getting-started/continuous_integration.md +271 -0
- local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/getting-started/getting_started.md +11 -0
- local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/getting-started/new-project-guide/rust_lang.md +148 -0
- local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/getting-started/new_project_guide.md +553 -0
- local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/oss-fuzz/architecture.md +33 -0
- local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/reference/glossary.md +99 -0
- local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/reference/reference.md +9 -0
local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/advanced-topics/advanced_topics.md
ADDED
|
@@ -0,0 +1,9 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Advanced topics
|
| 4 |
+
has_children: true
|
| 5 |
+
nav_order: 3
|
| 6 |
+
permalink: /advanced-topics/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Advanced topics
|
local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/advanced-topics/bug_fixing_guidance.md
ADDED
|
@@ -0,0 +1,94 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Bug fixing guidance
|
| 4 |
+
nav_order: 6
|
| 5 |
+
permalink: /advanced-topics/bug-fixing-guidance
|
| 6 |
+
---
|
| 7 |
+
|
| 8 |
+
# Bug fixing guidance
|
| 9 |
+
{: .no_toc}
|
| 10 |
+
|
| 11 |
+
This page provides brief guidance on how to prioritise and fix bugs reported by
|
| 12 |
+
OSS-Fuzz.
|
| 13 |
+
|
| 14 |
+
- TOC
|
| 15 |
+
{:toc}
|
| 16 |
+
|
| 17 |
+
## Threat modelling
|
| 18 |
+
In general the severity of an issue reported by OSS-Fuzz must be determined
|
| 19 |
+
relative to the threat model of the project under analysis. Therefore, although
|
| 20 |
+
the fuzzers OSS-Fuzz makes an effort into determining the severity of the bug
|
| 21 |
+
the true severity of the bug depends on the threat model of the project.
|
| 22 |
+
|
| 23 |
+
## Bug prioritisation
|
| 24 |
+
|
| 25 |
+
### Security issues
|
| 26 |
+
These are the top priority of solving. A label is attached to these on
|
| 27 |
+
the OSS-Fuzz testcase page and you can also search up all of these on monorail
|
| 28 |
+
using the search pattern `-Bug=security`.
|
| 29 |
+
|
| 30 |
+
Issues of this kind include issues reported by Address Sanitizer, e.g.
|
| 31 |
+
heap-based buffer overflows, stack-based buffer overflows and use-after-frees.
|
| 32 |
+
|
| 33 |
+
### Functional issues and memory leaks
|
| 34 |
+
These are issues that in general can tamper with the functionality of the
|
| 35 |
+
application. The bugs that have highest priority in this case are those that
|
| 36 |
+
can be easily triggered by an untrusted user of the project.
|
| 37 |
+
|
| 38 |
+
### Timeouts and out-of-memory
|
| 39 |
+
These are in general the least prioritised issues to solve.
|
| 40 |
+
|
| 41 |
+
### Bug prioritisation of non C/C++ projects
|
| 42 |
+
Currently there is no prioritisation of bugs in non C/C++ projects. As such, in
|
| 43 |
+
this scenario it is crucial you do the analysis yourself relative to the threat
|
| 44 |
+
model of your project.
|
| 45 |
+
|
| 46 |
+
## Non-reproducible bugs
|
| 47 |
+
OSS-Fuzz will report some bugs that are labeled `Reliably reproduces: NO` and
|
| 48 |
+
these can be tricky to deal with. A non-reproducible bug is an issue that
|
| 49 |
+
OSS-Fuzz did indeed discover, however, OSS-Fuzz is unable to reproduce the bug
|
| 50 |
+
with `python infra/helper.py reproduce`. In general, our suggestion is to do
|
| 51 |
+
analysis of the bug and determine whether there in fact is an issue.
|
| 52 |
+
|
| 53 |
+
The non-reproducible bugs can be of varying nature. Some of these bugs will be
|
| 54 |
+
due to some internal state of the target application being manipulated over the
|
| 55 |
+
cause of several executions of the fuzzer function. This could be several
|
| 56 |
+
hundreds or even thousands of executions and the bug may not be reproducible by
|
| 57 |
+
a single fuzzer test-case, however, there is indeed a bug in the application.
|
| 58 |
+
There are other reasons why bugs may be non-reproducible and in general any
|
| 59 |
+
non-determinism introduced into the application can have an effect on this.
|
| 60 |
+
|
| 61 |
+
In the case of non-reproducible bugs our advice is to put effort into analysing
|
| 62 |
+
the potential bug and also assess whether this is due to some internal state
|
| 63 |
+
that persists between each fuzz run. If that is indeed the case then we also
|
| 64 |
+
suggest investigating whether the fuzzer can be written such that the internal
|
| 65 |
+
state in the code will be reset between each fuzz run.
|
| 66 |
+
|
| 67 |
+
## Should all reported issues be solved?
|
| 68 |
+
It is reported by some project maintainers that fixing timeout issues reported
|
| 69 |
+
by OSS-Fuzz can increase the complexity of the project’s source code. The
|
| 70 |
+
result of this is that maintainers put effort into solving a timeout issue and
|
| 71 |
+
the fix results in additional complexity of the project. The question is
|
| 72 |
+
whether in a scenario like this if the overall result actually improves the
|
| 73 |
+
state of the application.
|
| 74 |
+
|
| 75 |
+
In order to answer this question we must assess the issue relative to the
|
| 76 |
+
threat model. Following the timeout anecdote then some timing issues can have
|
| 77 |
+
severe security implications. For example, if the timeout issue can cause
|
| 78 |
+
manipulation of control-flow then the timing issue may be of high security
|
| 79 |
+
severity. As such, it is difficult to say in the general case whether or not
|
| 80 |
+
some bugs should not be solved, as it should be analysed and determined on a
|
| 81 |
+
project-by-project basis.
|
| 82 |
+
|
| 83 |
+
In the event that a bug is reported by OSS-Fuzz that is not relevant to
|
| 84 |
+
security or reliability of the application then there may still be a point to
|
| 85 |
+
fixing the bug. For example, if the issue is often run into by the fuzzer then
|
| 86 |
+
the fuzzer may have difficulty exploring further code in the target, and thus
|
| 87 |
+
fixing the bug will allow the fuzzer to explore further code. In this case some
|
| 88 |
+
suggested examples of resolving the issue could be:
|
| 89 |
+
* Perform a hot-patch that is only applied during fuzzer executions and does
|
| 90 |
+
not overcomplicate the project’s code.
|
| 91 |
+
* Patch the code of the fuzzer to avoid the timeout. For example, some fuzzers
|
| 92 |
+
restrict the size of the input to avoid certain deep recursions or
|
| 93 |
+
time-intensive loops.
|
| 94 |
+
* Patch the code in the target despite complicating things.
|
local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/advanced-topics/code_coverage.md
ADDED
|
@@ -0,0 +1,130 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Code coverage
|
| 4 |
+
parent: Advanced topics
|
| 5 |
+
nav_order: 2
|
| 6 |
+
permalink: /advanced-topics/code-coverage/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Code Coverage
|
| 10 |
+
{: .no_toc}
|
| 11 |
+
|
| 12 |
+
For projects written in C/C++, Rust, Go, Swift or Java and other JVM-based languages,
|
| 13 |
+
you can generate code coverage reports using Clang source-based code coverage.
|
| 14 |
+
This page walks you through the basic steps.
|
| 15 |
+
For more details on C/C++ coverage, see [Clang's documentation].
|
| 16 |
+
|
| 17 |
+
Code coverage reports generation for other languages is not supported yet.
|
| 18 |
+
|
| 19 |
+
- TOC
|
| 20 |
+
{:toc}
|
| 21 |
+
---
|
| 22 |
+
|
| 23 |
+
## Pull the latest Docker images
|
| 24 |
+
|
| 25 |
+
Docker images get regularly updated with a newer version of build tools, build
|
| 26 |
+
configurations, scripts, and other changes. We recommend you pull the most
|
| 27 |
+
recent images by running the following command:
|
| 28 |
+
|
| 29 |
+
```bash
|
| 30 |
+
$ python infra/helper.py pull_images
|
| 31 |
+
```
|
| 32 |
+
|
| 33 |
+
## Build fuzz targets
|
| 34 |
+
|
| 35 |
+
Code coverage report generation requires a special build configuration to be
|
| 36 |
+
used. To create a code coverage build for your project, run these commands:
|
| 37 |
+
|
| 38 |
+
```bash
|
| 39 |
+
$ python infra/helper.py build_image $PROJECT_NAME
|
| 40 |
+
$ python infra/helper.py build_fuzzers --sanitizer=coverage $PROJECT_NAME
|
| 41 |
+
```
|
| 42 |
+
|
| 43 |
+
## Establish access to GCS
|
| 44 |
+
|
| 45 |
+
To get a good understanding of fuzz testing quality, you should generate code
|
| 46 |
+
coverage reports by running fuzz targets against the corpus
|
| 47 |
+
aggregated by OSS-Fuzz. Set up `gsutil` and ensure that you have access to the
|
| 48 |
+
corpora by doing the following:
|
| 49 |
+
|
| 50 |
+
* Install the [gsutil tool].
|
| 51 |
+
* Check whether you have access to the corpus for your project:
|
| 52 |
+
|
| 53 |
+
```bash
|
| 54 |
+
$ gsutil ls gs://${PROJECT_NAME}-corpus.clusterfuzz-external.appspot.com/
|
| 55 |
+
```
|
| 56 |
+
|
| 57 |
+
If you see an authorization error from the command above, run this:
|
| 58 |
+
|
| 59 |
+
```bash
|
| 60 |
+
$ gcloud auth login
|
| 61 |
+
```
|
| 62 |
+
|
| 63 |
+
and try again. Once `gsutil` works, you can run the report generation.
|
| 64 |
+
|
| 65 |
+
## Generate code coverage reports
|
| 66 |
+
|
| 67 |
+
### Full project report
|
| 68 |
+
|
| 69 |
+
If you want to generate a code coverage report using the corpus aggregated on
|
| 70 |
+
OSS-Fuzz, run this command:
|
| 71 |
+
|
| 72 |
+
```bash
|
| 73 |
+
$ python infra/helper.py coverage $PROJECT_NAME
|
| 74 |
+
```
|
| 75 |
+
|
| 76 |
+
If you want to generate a code coverage report using the corpus you have
|
| 77 |
+
locally, copy the corpus into the
|
| 78 |
+
`build/corpus/$PROJECT_NAME/<fuzz_target_name>/` directories for each fuzz
|
| 79 |
+
target, then run this command:
|
| 80 |
+
|
| 81 |
+
```bash
|
| 82 |
+
$ python infra/helper.py coverage --no-corpus-download $PROJECT_NAME
|
| 83 |
+
```
|
| 84 |
+
|
| 85 |
+
### Single fuzz target
|
| 86 |
+
|
| 87 |
+
You can generate a code coverage report for a particular fuzz target by using
|
| 88 |
+
the `--fuzz-target` argument:
|
| 89 |
+
|
| 90 |
+
```bash
|
| 91 |
+
$ python infra/helper.py coverage --fuzz-target=<fuzz_target_name> $PROJECT_NAME
|
| 92 |
+
```
|
| 93 |
+
|
| 94 |
+
In this mode, you can specify an arbitrary corpus location for the fuzz target
|
| 95 |
+
(instead of the corpus downloaded from OSS-Fuzz) by using `--corpus-dir`:
|
| 96 |
+
|
| 97 |
+
```bash
|
| 98 |
+
$ python infra/helper.py coverage --fuzz-target=<fuzz_target_name> \
|
| 99 |
+
--corpus-dir=<my_local_corpus_dir> $PROJECT_NAME
|
| 100 |
+
```
|
| 101 |
+
|
| 102 |
+
### Additional arguments for `llvm-cov` (C/C++/Rust only)
|
| 103 |
+
|
| 104 |
+
You may want to use some of the options provided by the [llvm-cov tool], like
|
| 105 |
+
`-ignore-filename-regex=`. You can pass these to the helper script after `--`:
|
| 106 |
+
|
| 107 |
+
```bash
|
| 108 |
+
$ python infra/helper.py coverage $PROJECT_NAME -- \
|
| 109 |
+
-ignore-filename-regex=.*code/to/be/ignored/.* <other_extra_args>
|
| 110 |
+
```
|
| 111 |
+
|
| 112 |
+
If you want to specify particular source files or directories to show in the
|
| 113 |
+
report, list their paths at the end of the extra arguments sequence:
|
| 114 |
+
|
| 115 |
+
```bash
|
| 116 |
+
$ python infra/helper.py coverage zlib -- \
|
| 117 |
+
<other_extra_args> /src/zlib/inftrees.c /src/zlib_uncompress_fuzzer.cc /src/zlib/zutil.c
|
| 118 |
+
```
|
| 119 |
+
|
| 120 |
+
If you want OSS-Fuzz to use extra arguments when generating code coverage
|
| 121 |
+
reports for your project, add the arguments into your `project.yaml` file as
|
| 122 |
+
follows:
|
| 123 |
+
|
| 124 |
+
```yaml
|
| 125 |
+
coverage_extra_args: -ignore-filename-regex=.*crc.* -ignore-filename-regex=.*adler.* <other_extra_args>
|
| 126 |
+
```
|
| 127 |
+
|
| 128 |
+
[Clang's documentation]: https://clang.llvm.org/docs/SourceBasedCodeCoverage.html
|
| 129 |
+
[gsutil tool]: https://cloud.google.com/storage/docs/gsutil_install
|
| 130 |
+
[llvm-cov tool]: https://llvm.org/docs/CommandGuide/llvm-cov.html
|
local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/advanced-topics/corpora.md
ADDED
|
@@ -0,0 +1,70 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Corpora
|
| 4 |
+
parent: Advanced topics
|
| 5 |
+
nav_order: 3
|
| 6 |
+
permalink: /advanced-topics/corpora/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Accessing Corpora
|
| 10 |
+
{: .no_toc}
|
| 11 |
+
|
| 12 |
+
If you want to access the corpora that we are using for your fuzz targets
|
| 13 |
+
(synthesized by the fuzzing engines), follow these steps.
|
| 14 |
+
|
| 15 |
+
- TOC
|
| 16 |
+
{:toc}
|
| 17 |
+
---
|
| 18 |
+
|
| 19 |
+
## Obtain access
|
| 20 |
+
|
| 21 |
+
To get access to a project's corpora, you must be listed as the
|
| 22 |
+
primary contact or as an auto cc in the project's `project.yaml` file, as described
|
| 23 |
+
in the [New Project Guide]({{ site.baseurl }}/getting-started/new-project-guide/#projectyaml).
|
| 24 |
+
If you don't do this, most of the links below won't work.
|
| 25 |
+
|
| 26 |
+
## Install Google Cloud SDK
|
| 27 |
+
|
| 28 |
+
The corpora for fuzz targets are stored on [Google Cloud
|
| 29 |
+
Storage](https://cloud.google.com/storage/). To access them, you need to
|
| 30 |
+
[install the gsutil
|
| 31 |
+
tool](https://cloud.google.com/storage/docs/gsutil_install), which is part of
|
| 32 |
+
the Google Cloud SDK. Follow the instructions on the installation page to
|
| 33 |
+
login with the Google account listed in your project's `project.yaml` file.
|
| 34 |
+
|
| 35 |
+
## Viewing the corpus for a fuzz target
|
| 36 |
+
|
| 37 |
+
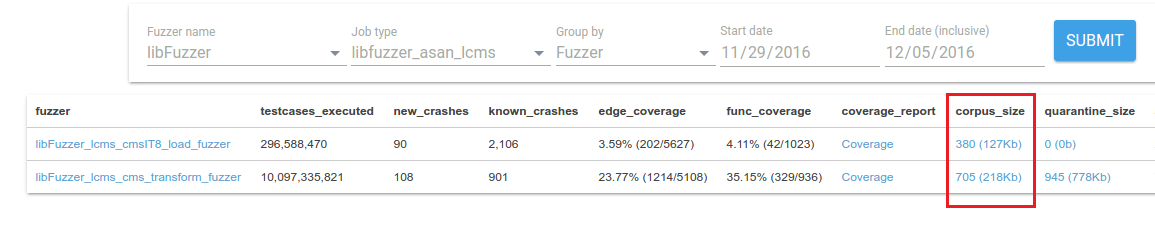
The fuzzer statistics page for your project on
|
| 38 |
+
[ClusterFuzz]({{ site.baseurl }}/further-reading/clusterfuzz)
|
| 39 |
+
contains a link to the Google Cloud console for your corpus under the
|
| 40 |
+
**corpus_size** column. Click the link to browse and download individual test inputs in the
|
| 41 |
+
corpus.
|
| 42 |
+
|
| 43 |
+
|
| 44 |
+
|
| 45 |
+
## Downloading the corpus
|
| 46 |
+
|
| 47 |
+
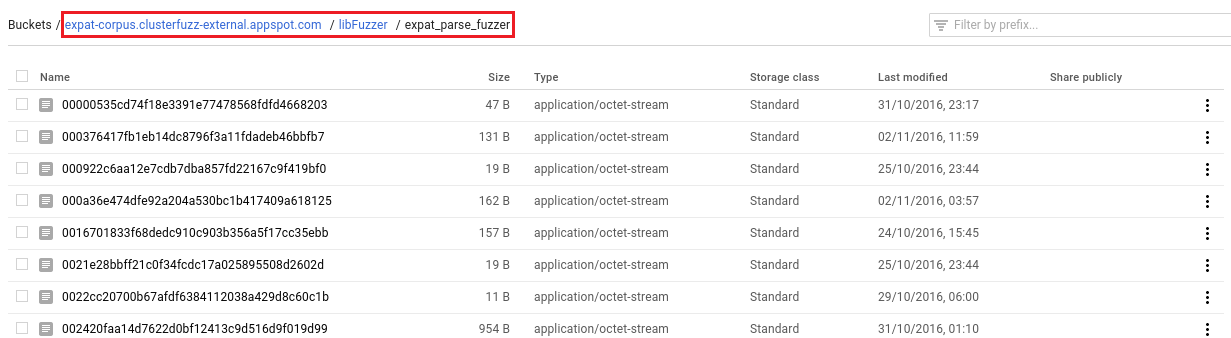
If you want to download the entire corpus, click the link in the **corpus_size** column, then
|
| 48 |
+
copy the **Buckets** path at the top of the page:
|
| 49 |
+
|
| 50 |
+
|
| 51 |
+
|
| 52 |
+
Copy the corpus to a directory on your
|
| 53 |
+
machine by running the following command:
|
| 54 |
+
|
| 55 |
+
```bash
|
| 56 |
+
$ gsutil -m cp -r gs://<bucket_path> <local_directory>
|
| 57 |
+
```
|
| 58 |
+
Using the expat example above, this would be:
|
| 59 |
+
|
| 60 |
+
```bash
|
| 61 |
+
$ gsutil -m cp -r \
|
| 62 |
+
gs://expat-corpus.clusterfuzz-external.appspot.com/libFuzzer/expat_parse_fuzzer \
|
| 63 |
+
<local_directory>
|
| 64 |
+
```
|
| 65 |
+
|
| 66 |
+
## Corpus backups
|
| 67 |
+
|
| 68 |
+
We keep daily zipped backups of your corpora. These can be accessed from the
|
| 69 |
+
**corpus_backup** column of the fuzzer statistics page. Downloading these can
|
| 70 |
+
be significantly faster than running `gsutil -m cp -r` on the corpus bucket.
|
local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/advanced-topics/debugging.md
ADDED
|
@@ -0,0 +1,45 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Debugging
|
| 4 |
+
parent: Advanced topics
|
| 5 |
+
nav_order: 4
|
| 6 |
+
permalink: /advanced-topics/debugging/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Debugging issues
|
| 10 |
+
{: .no_toc}
|
| 11 |
+
|
| 12 |
+
- TOC
|
| 13 |
+
{:toc}
|
| 14 |
+
---
|
| 15 |
+
|
| 16 |
+
## Debugging build scripts
|
| 17 |
+
|
| 18 |
+
While developing your build script, it may be useful to run bash within the
|
| 19 |
+
container:
|
| 20 |
+
|
| 21 |
+
```bash
|
| 22 |
+
$ python infra/helper.py shell $PROJECT_NAME # runs /bin/bash within container
|
| 23 |
+
$ compile # runs compilation manually
|
| 24 |
+
```
|
| 25 |
+
|
| 26 |
+
## Debugging fuzzers with GDB
|
| 27 |
+
|
| 28 |
+
If you wish to debug a fuzz target with gdb, you can use the base-runner-debug
|
| 29 |
+
image:
|
| 30 |
+
|
| 31 |
+
```bash
|
| 32 |
+
# Copy input testcase into host output directory so it can be accessed
|
| 33 |
+
# within the Docker image.
|
| 34 |
+
$ cp /path/to/testcase build/out/$PROJECT_NAME
|
| 35 |
+
|
| 36 |
+
# Run the Docker image containing GDB.
|
| 37 |
+
$ python infra/helper.py shell base-runner-debug
|
| 38 |
+
$ gdb --args /out/$PROJECT_NAME/$FUZZ_TARGET_NAME /out/$PROJECT_NAME/testcase
|
| 39 |
+
```
|
| 40 |
+
|
| 41 |
+
**Note:** The `base-runner-debug` image does not have access to your sources, so
|
| 42 |
+
you will not be able to do source code level debugging. We recommend integrating
|
| 43 |
+
your fuzz target upstream as part of
|
| 44 |
+
[ideal integration]({{ site.baseurl }}/advanced-topics/ideal-integration/)
|
| 45 |
+
for debugging purposes.
|
local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/advanced-topics/fuzz_introspector.md
ADDED
|
@@ -0,0 +1,118 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Fuzz Introspector
|
| 4 |
+
parent: Advanced topics
|
| 5 |
+
nav_order: 2
|
| 6 |
+
permalink: /advanced-topics/fuzz-introspector/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Fuzz Introspector
|
| 10 |
+
{: .no_toc}
|
| 11 |
+
|
| 12 |
+
For projects written in C/C++, Python and Java you can generate Fuzz
|
| 13 |
+
Introspector reports to help guide the development of your fuzzing suite.
|
| 14 |
+
These reports help to extract details about the fuzzing setup of your
|
| 15 |
+
project with the goal of making it easier to improve the fuzzing set up.
|
| 16 |
+
The Fuzz Introspector reports are generated automatically and uploaded
|
| 17 |
+
to the cloud like code coverage reports, and you can also generate them
|
| 18 |
+
locally using the OSS-Fuzz helper script.
|
| 19 |
+
|
| 20 |
+
|
| 21 |
+
- TOC
|
| 22 |
+
{:toc}
|
| 23 |
+
---
|
| 24 |
+
|
| 25 |
+
## Fuzz Introspector overview
|
| 26 |
+
|
| 27 |
+
As soon as your project is run with ClusterFuzz (<1 day), you can view the Fuzz
|
| 28 |
+
Introspector report for your project.
|
| 29 |
+
[Fuzz Introspector](https://github.com/ossf/fuzz-introspector) helps you
|
| 30 |
+
understand your fuzzers' performance and identify any potential blockers.
|
| 31 |
+
It provides individual and aggregated fuzzer reachability and coverage reports.
|
| 32 |
+
You can monitor each fuzzer's static reachability potential and compare it
|
| 33 |
+
against dynamic coverage and identify any potential bottlenecks.
|
| 34 |
+
Fuzz Introspector can offer suggestions on increasing coverage by adding new
|
| 35 |
+
fuzz targets or modify existing ones.
|
| 36 |
+
Fuzz Introspector reports can be viewed from the [OSS-Fuzz
|
| 37 |
+
homepage](https://oss-fuzz.com/) or through this
|
| 38 |
+
[index](http://oss-fuzz-introspector.storage.googleapis.com/index.html).
|
| 39 |
+
|
| 40 |
+
- [Fuzz Introspector documentation](https://fuzz-introspector.readthedocs.io/en/latest/)
|
| 41 |
+
- [Fuzz Introspector source code](https://github.com/ossf/fuzz-introspector)
|
| 42 |
+
- [OSS-Fuzz Fuzz Introspector reports](http://oss-fuzz-introspector.storage.googleapis.com/index.html)
|
| 43 |
+
|
| 44 |
+
|
| 45 |
+
## Tutorials and guides
|
| 46 |
+
|
| 47 |
+
The reports generated can be a lot to digest when first viewing them. The
|
| 48 |
+
[Fuzz Introspector documentation](https://fuzz-introspector.readthedocs.io/en/latest/)
|
| 49 |
+
provides various user guides and tutorials rooted in OSS-Fuzz projects, which is
|
| 50 |
+
a useful reference on how to make use of the reports.
|
| 51 |
+
|
| 52 |
+
For ideas on how to use Fuzz Introspector, see [user guides](https://fuzz-introspector.readthedocs.io/en/latest/user-guides/index.html) which includes sections e.g.
|
| 53 |
+
- [Quickly extract overview of a given project](https://fuzz-introspector.readthedocs.io/en/latest/user-guides/quick-overview.html)
|
| 54 |
+
- [Get ideas for new fuzz targets](https://fuzz-introspector.readthedocs.io/en/latest/user-guides/get-ideas-for-new-targets.html)
|
| 55 |
+
- [Comparing introspector reports](https://fuzz-introspector.readthedocs.io/en/latest/user-guides/comparing-introspector-reports.html)
|
| 56 |
+
|
| 57 |
+
## Run Fuzz Introspector locally
|
| 58 |
+
|
| 59 |
+
To generate a Fuzz Introspector report locally use `infra/helper.py` and the
|
| 60 |
+
`introspector` command. Fuzz Introspector relies on code coverage to
|
| 61 |
+
analyze a given project, and this means we need to extract code coverage in the
|
| 62 |
+
Fuzz Introspector process. We can do this in two ways. First, by running the fuzzers
|
| 63 |
+
for a given amount of time, and, second, by generating code coverage using the public
|
| 64 |
+
corpus available from OSS-Fuzz.
|
| 65 |
+
|
| 66 |
+
|
| 67 |
+
### Generate reports by running fuzzers for X seconds
|
| 68 |
+
|
| 69 |
+
The following command will generate a Fuzz Introspector report for the `libdwarf` project
|
| 70 |
+
and will extract code coverage based on a corpus created from running the fuzzers for 30
|
| 71 |
+
seconds.
|
| 72 |
+
|
| 73 |
+
```bash
|
| 74 |
+
$ python3 infra/helper.py introspector libdwarf --seconds=30
|
| 75 |
+
```
|
| 76 |
+
|
| 77 |
+
If the above command was succesful, you should see output along the lines of:
|
| 78 |
+
|
| 79 |
+
```bash
|
| 80 |
+
INFO:root:To browse the report, run: python3 -m http.server 8008 --directory /home/my_user/oss-fuzz/build/out/libdwarf/introspector-report/inspector and navigate to localhost:8008/fuzz_report.html in your browser
|
| 81 |
+
```
|
| 82 |
+
The above output gives you directions on how to start a simple webserver using
|
| 83 |
+
`python3 -m http.server`, which you can use to view the Fuzz Introspector report.
|
| 84 |
+
|
| 85 |
+
### Generate reports by using public corpora
|
| 86 |
+
|
| 87 |
+
The following command will generate a Fuzz Introspector report for the `libdwarf` project
|
| 88 |
+
and will extract code coverage based on the publicly available corpora.
|
| 89 |
+
|
| 90 |
+
```bash
|
| 91 |
+
$ python3 infra/helper.py introspector libdwarf --public-corpora
|
| 92 |
+
```
|
| 93 |
+
|
| 94 |
+
Assuming the above command is succesful you can view the report using `python3 -m http.server`
|
| 95 |
+
following the example described above.
|
| 96 |
+
|
| 97 |
+
|
| 98 |
+
## Differences in build tooling
|
| 99 |
+
|
| 100 |
+
There are some differences in build environment for Fuzz Introspector builds
|
| 101 |
+
in comparison to e.g. ASAN or code coverage builds. The reason is that
|
| 102 |
+
Fuzz Introspector relies on certain compile-time tools to do its analysis.
|
| 103 |
+
This compile time tooling differs between languages, namely:
|
| 104 |
+
- For C/C++, Fuzz Introspector relies on [LLVM LTO](https://llvm.org/docs/LinkTimeOptimization.html) and [LLVM Gold](https://llvm.org/docs/GoldPlugin.html)
|
| 105 |
+
- For Python, Fuzz Introspector relies on a modified [PyCG](https://github.com/vitsalis/PyCG)
|
| 106 |
+
- For Java, Fuzz Introspector relies on [Soot](https://soot-oss.github.io/soot/)
|
| 107 |
+
|
| 108 |
+
The consequence of this is your project must be compatible with these projects.
|
| 109 |
+
PyCG and Soot have not shown to be a blocker for many projects, however, experience
|
| 110 |
+
has shown that sometimes a project's build needs modification in order to compile
|
| 111 |
+
with LLVM LTO. The easiest way to test if your project works with LLVM is checking
|
| 112 |
+
whether your project can compile with the flags `-flto -fuse-ld=gold` and using
|
| 113 |
+
the gold linker. OSS-Fuzz automatically sets these flags and linker options when
|
| 114 |
+
using `infra/helper.py` to build your project with `--sanitizer=introspector`, e.g.
|
| 115 |
+
|
| 116 |
+
```bash
|
| 117 |
+
python3 infra/helper.py build_fuzzers --sanitizer=introspector PROJ_NAME
|
| 118 |
+
```
|
local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/advanced-topics/ideal_integration.md
ADDED
|
@@ -0,0 +1,174 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Ideal integration
|
| 4 |
+
parent: Advanced topics
|
| 5 |
+
nav_order: 1
|
| 6 |
+
permalink: /advanced-topics/ideal-integration/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Ideal integration with OSS-Fuzz
|
| 10 |
+
{: .no_toc}
|
| 11 |
+
|
| 12 |
+
OSS projects have different build and test systems. We can't expect them all to
|
| 13 |
+
implement and maintain fuzz targets or integrate them with OSS-Fuzz in the same
|
| 14 |
+
way. However, we do have recommendations.
|
| 15 |
+
|
| 16 |
+
This page documents several features (starting from the easiest) that will make
|
| 17 |
+
automated fuzzing simple and efficient, and will help you catch regressions
|
| 18 |
+
early in the development cycle. This simple
|
| 19 |
+
[example](https://github.com/google/oss-fuzz/tree/master/projects/example/my-api-repo)
|
| 20 |
+
covers most of the items.
|
| 21 |
+
|
| 22 |
+
- TOC
|
| 23 |
+
{:toc}
|
| 24 |
+
---
|
| 25 |
+
|
| 26 |
+
## Summary
|
| 27 |
+
|
| 28 |
+
Every [fuzz target](https://llvm.org/docs/LibFuzzer.html#fuzz-target):
|
| 29 |
+
* Is [maintained by code owners](#fuzz-target) in their RCS (Git, SVN, etc).
|
| 30 |
+
* Is [built with the rest of the tests](#build-support) - no bit rot!
|
| 31 |
+
* Has a [seed corpus](#seed-corpus) with good [code coverage](#coverage).
|
| 32 |
+
* Has a [dictionary](#dictionary), if applicable.
|
| 33 |
+
* Is [continuously tested on the seed corpus](#regression-testing) with
|
| 34 |
+
[ASan/UBSan/MSan](https://github.com/google/sanitizers).
|
| 35 |
+
* Is [fast and has no OOMs](#performance).
|
| 36 |
+
|
| 37 |
+
## Fuzz Target
|
| 38 |
+
|
| 39 |
+
The code of the [fuzz target(s)](https://llvm.org/docs/LibFuzzer.html#fuzz-target) should be
|
| 40 |
+
part of the project's source code repository. All fuzz targets should be easily
|
| 41 |
+
discoverable (reside in the same directory, follow the same naming pattern,
|
| 42 |
+
etc.).
|
| 43 |
+
|
| 44 |
+
This makes it easy to maintain the fuzzers and minimizes breakages that can
|
| 45 |
+
arise as source code changes over time.
|
| 46 |
+
|
| 47 |
+
Make sure to fuzz the target locally for a small period of time to ensure that
|
| 48 |
+
it does not crash, hang, or run out of memory instantly. Also make sure that the fuzzer can
|
| 49 |
+
make at least some progress. If you're having trouble, read about [what makes a good fuzz
|
| 50 |
+
target](https://github.com/google/fuzzing/blob/master/docs/good-fuzz-target.md).
|
| 51 |
+
|
| 52 |
+
The interface between the [fuzz target](https://llvm.org/docs/LibFuzzer.html#fuzz-target)
|
| 53 |
+
and the fuzzing engines is C, so you can use either C or C++ to implement the
|
| 54 |
+
fuzz target. Make sure to not return values other than **zero** [^1].
|
| 55 |
+
|
| 56 |
+
Examples:
|
| 57 |
+
[boringssl](https://github.com/google/boringssl/tree/master/fuzz),
|
| 58 |
+
[SQLite](https://www.sqlite.org/src/artifact/ad79e867fb504338),
|
| 59 |
+
[s2n](https://github.com/awslabs/s2n/tree/master/tests/fuzz),
|
| 60 |
+
[openssl](https://github.com/openssl/openssl/tree/master/fuzz),
|
| 61 |
+
[FreeType](http://git.savannah.gnu.org/cgit/freetype/freetype2.git/tree/src/tools/ftfuzzer),
|
| 62 |
+
[re2](https://github.com/google/re2/tree/master/re2/fuzzing),
|
| 63 |
+
[harfbuzz](https://github.com/behdad/harfbuzz/tree/master/test/fuzzing),
|
| 64 |
+
[pcre2](https://vcs.pcre.org/pcre2/code/trunk/src/pcre2_fuzzsupport.c?view=markup),
|
| 65 |
+
[ffmpeg](https://github.com/FFmpeg/FFmpeg/blob/master/tools/target_dec_fuzzer.c).
|
| 66 |
+
|
| 67 |
+
[^1]: While LibFuzzer uses a non-zero value as a signal to discard inputs other fuzzers in
|
| 68 |
+
use by OSS-Fuzz do not necessarily support this behavior. (Discarding inputs can be used
|
| 69 |
+
to stop a fuzzer from exploring further, which should only be used with good reason.)
|
| 70 |
+
|
| 71 |
+
## Build support
|
| 72 |
+
|
| 73 |
+
Many different build systems exist in the open-source world. The less OSS-Fuzz
|
| 74 |
+
knows about them, the better it can scale.
|
| 75 |
+
|
| 76 |
+
An ideal build integration for OSS-Fuzz looks like this:
|
| 77 |
+
* For every fuzz target `foo` in the project, there is a build rule that
|
| 78 |
+
builds `foo_fuzzer`, a binary that:
|
| 79 |
+
* Contains the fuzzing entry point.
|
| 80 |
+
* Contains (`LLVMFuzzerTestOneInput`) and all the code it depends on.
|
| 81 |
+
* Uses the `main()` function from `$LIB_FUZZING_ENGINE` (env var [provided]({{ site.baseurl }}/getting-started/new-project-guide/) by OSS-Fuzz environment).
|
| 82 |
+
* Since the build system supports changing the compiler and passing extra compiler
|
| 83 |
+
flags, the build command for `foo_fuzzer` looks similar to this:
|
| 84 |
+
|
| 85 |
+
```bash
|
| 86 |
+
# Assume the following env vars are set:
|
| 87 |
+
# CC, CXX, CFLAGS, CXXFLAGS, LIB_FUZZING_ENGINE
|
| 88 |
+
$ make_or_whatever_other_command foo_fuzzer
|
| 89 |
+
```
|
| 90 |
+
|
| 91 |
+
This minimizes OSS-Fuzz-specific configuration, making your fuzzing more robust.
|
| 92 |
+
|
| 93 |
+
There is no point in hardcoding the exact compiler flags in the build system
|
| 94 |
+
because they a) may change and b) depend on the fuzzing engine and sanitizer
|
| 95 |
+
being used.
|
| 96 |
+
|
| 97 |
+
## Seed Corpus
|
| 98 |
+
|
| 99 |
+
The *seed corpus* is a set of test inputs, stored as individual files, provided
|
| 100 |
+
to the fuzz target as a starting point (to "seed" the mutations). The quality of
|
| 101 |
+
the seed corpus has a huge impact on fuzzing efficiency; the higher the quality,
|
| 102 |
+
the easier it is for the fuzzer to discover new code paths. The ideal corpus is
|
| 103 |
+
a minimal set of inputs that provides maximal code coverage.
|
| 104 |
+
|
| 105 |
+
For better OSS-Fuzz integration, the seed corpus should be available in
|
| 106 |
+
revision control (it can be the same as or different from the source code). It
|
| 107 |
+
should be regularly extended with the inputs that (used to) trigger bugs and/or
|
| 108 |
+
touch new parts of the code.
|
| 109 |
+
|
| 110 |
+
Examples:
|
| 111 |
+
[boringssl](https://github.com/google/boringssl/tree/master/fuzz),
|
| 112 |
+
[openssl](https://github.com/openssl/openssl/tree/master/fuzz),
|
| 113 |
+
[nss](https://github.com/mozilla/nss-fuzzing-corpus) (corpus in a separate repo).
|
| 114 |
+
|
| 115 |
+
## Dictionary
|
| 116 |
+
|
| 117 |
+
For some input types, a simple dictionary of tokens used by the input language
|
| 118 |
+
can have a dramatic impact on fuzzing efficiency. For example, when fuzzing an
|
| 119 |
+
XML parser, a dictionary of XML tokens is helpful. AFL++ has a
|
| 120 |
+
[collection](https://github.com/AFLplusplus/AFLplusplus/tree/master/dictionaries)
|
| 121 |
+
of dictionaries for popular data formats. Ideally, a dictionary should be
|
| 122 |
+
maintained alongside the fuzz target, and it must use [correct
|
| 123 |
+
syntax](https://llvm.org/docs/LibFuzzer.html#dictionaries).
|
| 124 |
+
|
| 125 |
+
## Coverage
|
| 126 |
+
|
| 127 |
+
For a fuzz target to be useful, it must have good coverage in the code that it
|
| 128 |
+
is testing. You can view the coverage for your fuzz targets by looking at the
|
| 129 |
+
[fuzzer stats]({{ site.baseurl }}/further-reading/clusterfuzz#fuzzer-stats)
|
| 130 |
+
dashboard on ClusterFuzz, as well as [coverage reports]({{ site.baseurl
|
| 131 |
+
}}/further-reading/clusterfuzz#coverage-reports).
|
| 132 |
+
|
| 133 |
+
To generate an aggregated code coverage report for your project, please see the
|
| 134 |
+
[code coverage]({{ site.baseurl }}/advanced-topics/code-coverage) page.
|
| 135 |
+
|
| 136 |
+
Coverage can often be improved by adding dictionaries, more inputs for seed
|
| 137 |
+
corpora, and fixing timeouts/out-of-memory bugs in your targets.
|
| 138 |
+
|
| 139 |
+
## Regression Testing
|
| 140 |
+
|
| 141 |
+
Fuzz targets should be regularly tested (not necessarily fuzzed!) as a part of
|
| 142 |
+
the project's regression testing process. One way to do so is to link the fuzz
|
| 143 |
+
target with a simple standalone driver
|
| 144 |
+
([example](https://github.com/llvm-mirror/compiler-rt/tree/master/lib/fuzzer/standalone))
|
| 145 |
+
that runs the provided inputs, then use this driver with the seed corpus created
|
| 146 |
+
in previous step. We recommend you use
|
| 147 |
+
[sanitizers](https://github.com/google/sanitizers) during regression testing.
|
| 148 |
+
|
| 149 |
+
Examples: [SQLite](https://www.sqlite.org/src/artifact/d9f1a6f43e7bab45),
|
| 150 |
+
[openssl](https://github.com/openssl/openssl/blob/master/fuzz/test-corpus.c).
|
| 151 |
+
|
| 152 |
+
## Performance
|
| 153 |
+
|
| 154 |
+
Fuzz targets should perform well, because high memory usage and/or slow
|
| 155 |
+
execution speed can slow the down the growth of coverage and finding of new
|
| 156 |
+
bugs. ClusterFuzz provides a [performance analyzer]({{ site.baseurl
|
| 157 |
+
}}/further-reading/clusterfuzz/#performance-analyzer) for each fuzz target that
|
| 158 |
+
shows problems that are impacting performance.
|
| 159 |
+
|
| 160 |
+
## Not a project member?
|
| 161 |
+
|
| 162 |
+
If you are a member of the project you want to fuzz, most of the steps above are
|
| 163 |
+
simple. However in some cases, someone outside the project team may want to fuzz
|
| 164 |
+
the code, and the project maintainers are not interested in helping.
|
| 165 |
+
|
| 166 |
+
In such cases, we can host the fuzz targets, dictionaries, etc. in OSS-Fuzz's
|
| 167 |
+
repository and mention them in the Dockerfile. It's not ideal, because the fuzz
|
| 168 |
+
targets will not be continuously tested, so may quickly bitrot.
|
| 169 |
+
|
| 170 |
+
Examples: [libxml2](https://github.com/google/oss-fuzz/tree/master/projects/libxml2),
|
| 171 |
+
[c-ares](https://github.com/google/oss-fuzz/tree/master/projects/c-ares), [expat](https://github.com/google/oss-fuzz/tree/master/projects/expat).
|
| 172 |
+
|
| 173 |
+
If you are not a project maintainer, we may not be able to CC you to security
|
| 174 |
+
bugs found by OSS-Fuzz.
|
local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/advanced-topics/reproducing.md
ADDED
|
@@ -0,0 +1,160 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Reproducing
|
| 4 |
+
parent: Advanced topics
|
| 5 |
+
nav_order: 5
|
| 6 |
+
permalink: /advanced-topics/reproducing/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Reproducing OSS-Fuzz issues
|
| 10 |
+
{: .no_toc}
|
| 11 |
+
|
| 12 |
+
You've been CCed on an OSS-Fuzz issue
|
| 13 |
+
([examples](https://bugs.chromium.org/p/oss-fuzz/issues/list?can=1&q=Type%3ABug%2CBug-Security)).
|
| 14 |
+
Now what? Before attempting to fix the bug, you should be able to reliably
|
| 15 |
+
reproduce it.
|
| 16 |
+
|
| 17 |
+
- TOC
|
| 18 |
+
{:toc}
|
| 19 |
+
---
|
| 20 |
+
|
| 21 |
+
## Fuzz target bugs
|
| 22 |
+
|
| 23 |
+
Every issue has a [reproducer file]({{ site.baseurl
|
| 24 |
+
}}/reference/glossary/#reproducer) (also know as a "testcase" file) attached.
|
| 25 |
+
Download it. This file contains the bytes that were fed to the [fuzz
|
| 26 |
+
target](https://llvm.org/docs/LibFuzzer.html#fuzz-target).
|
| 27 |
+
|
| 28 |
+
**Note:** If the issue is not public, you will need to login using a
|
| 29 |
+
[Google account](https://support.google.com/accounts/answer/176347?hl=en)
|
| 30 |
+
([why?]({{ site.baseurl
|
| 31 |
+
}}/faq/#why-do-you-require-a-google-account-for-authentication)) that the bug
|
| 32 |
+
report CCs.
|
| 33 |
+
|
| 34 |
+
If you have already
|
| 35 |
+
[integrated]({{ site.baseurl }}/advanced-topics/ideal-integration/)
|
| 36 |
+
the fuzz target with your build and test system, all you have to do is run this command:
|
| 37 |
+
```bash
|
| 38 |
+
$ ./fuzz_target_binary <testcase_path>
|
| 39 |
+
```
|
| 40 |
+
|
| 41 |
+
For timeout bugs, add the `-timeout=65` argument. For OOM bugs, add the
|
| 42 |
+
`-rss_limit_mb=2560` argument. Read more on [how timeouts and OOMs are
|
| 43 |
+
handled]({{ site.baseurl }}/faq/#how-do-you-handle-timeouts-and-ooms).
|
| 44 |
+
|
| 45 |
+
Depending on the nature of the bug, the fuzz target binary needs to be built
|
| 46 |
+
with the appropriate [sanitizer](https://github.com/google/sanitizers)
|
| 47 |
+
(for example, if it's a buffer overflow, build with
|
| 48 |
+
[AddressSanitizer](http://clang.llvm.org/docs/AddressSanitizer.html)).
|
| 49 |
+
|
| 50 |
+
If you're not sure how to build the fuzzer using the project's build system,
|
| 51 |
+
you can also use Docker commands to replicate the exact build steps used by
|
| 52 |
+
OSS-Fuzz, then feed the reproducer input to the fuzz target ([how?]({{
|
| 53 |
+
site.baseurl }}/getting-started/new-project-guide/#prerequisites), [why?]({{
|
| 54 |
+
site.baseurl }}/faq/#why-do-you-use-docker)).
|
| 55 |
+
|
| 56 |
+
## Building using Docker
|
| 57 |
+
|
| 58 |
+
### Cloning OSS-Fuzz
|
| 59 |
+
|
| 60 |
+
To use the following `infra/helper.py` commands, you need a checkout of OSS-Fuzz:
|
| 61 |
+
|
| 62 |
+
```bash
|
| 63 |
+
$ git clone --depth=1 https://github.com/google/oss-fuzz.git
|
| 64 |
+
$ cd oss-fuzz
|
| 65 |
+
```
|
| 66 |
+
|
| 67 |
+
### Pull the latest Docker images
|
| 68 |
+
|
| 69 |
+
Docker images get regularly updated with a newer version of build tools, build
|
| 70 |
+
configurations, scripts, and other changes. In some cases, a particular issue
|
| 71 |
+
can be reproduced only with a fresh image being used. Pull the latest images
|
| 72 |
+
by running the following command:
|
| 73 |
+
|
| 74 |
+
```bash
|
| 75 |
+
$ python infra/helper.py pull_images
|
| 76 |
+
```
|
| 77 |
+
|
| 78 |
+
### Build the image and the fuzzers
|
| 79 |
+
|
| 80 |
+
Run the following commands:
|
| 81 |
+
|
| 82 |
+
```bash
|
| 83 |
+
$ python infra/helper.py build_image $PROJECT_NAME
|
| 84 |
+
$ python infra/helper.py build_fuzzers --sanitizer <address/memory/undefined> \
|
| 85 |
+
--architecture <x86_64/i386> $PROJECT_NAME
|
| 86 |
+
```
|
| 87 |
+
|
| 88 |
+
The `sanitizer` used in the report is the value in the
|
| 89 |
+
**Sanitizer** column. It's one of the following:
|
| 90 |
+
* **address** for AddressSanitizer.
|
| 91 |
+
* **memory** for MemorySanitizer.
|
| 92 |
+
* **undefined** for UndefinedBehaviorSanitizer.
|
| 93 |
+
|
| 94 |
+
**Notes**:
|
| 95 |
+
* The `architecture` argument is only necessary if you want to specify
|
| 96 |
+
`i386` configuration.
|
| 97 |
+
* Some bugs (specially ones related to pointer and integer overflows) are reproducible only in 32 bit mode or only in 64 bit mode.
|
| 98 |
+
If you can't reproduce a particular bug building for x86_64, try building for i386.
|
| 99 |
+
|
| 100 |
+
## Reproducing bugs
|
| 101 |
+
|
| 102 |
+
After you build an image and a fuzzer, you can reproduce a bug by running the following command:
|
| 103 |
+
|
| 104 |
+
```bash
|
| 105 |
+
$ python infra/helper.py reproduce $PROJECT_NAME <fuzz_target_name> <testcase_path>
|
| 106 |
+
```
|
| 107 |
+
|
| 108 |
+
For example, to build the [libxml2](https://github.com/google/oss-fuzz/tree/master/projects/libxml2)
|
| 109 |
+
project with UndefinedBehaviorSanitizer (`undefined`) instrumentation and
|
| 110 |
+
reproduce a crash testcase for a fuzzer named `libxml2_xml_read_memory_fuzzer`,
|
| 111 |
+
you would run:
|
| 112 |
+
|
| 113 |
+
```bash
|
| 114 |
+
$ python infra/helper.py build_image libxml2
|
| 115 |
+
$ python infra/helper.py build_fuzzers --sanitizer undefined libxml2
|
| 116 |
+
$ python infra/helper.py reproduce libxml2 libxml2_xml_read_memory_fuzzer ~/Downloads/testcase
|
| 117 |
+
```
|
| 118 |
+
|
| 119 |
+
## Reproduce using local source checkout
|
| 120 |
+
|
| 121 |
+
You can also mount local sources into the running container by using these commands:
|
| 122 |
+
|
| 123 |
+
```bash
|
| 124 |
+
$ python infra/helper.py build_fuzzers \
|
| 125 |
+
--sanitizer <address/memory/undefined> $PROJECT_NAME <source_path>
|
| 126 |
+
$ python infra/helper.py reproduce $PROJECT_NAME <fuzz_target_name> <testcase_path>
|
| 127 |
+
```
|
| 128 |
+
|
| 129 |
+
Once you reproduce the bug, you can do the following:
|
| 130 |
+
|
| 131 |
+
- **Fix issue:** Write a patch to fix the issue in your local checkout, then
|
| 132 |
+
use the previous command to verify the fix (i.e. no crash occurred).
|
| 133 |
+
[Use gdb]({{ site.baseurl }}/advanced-topics/debugging/#debugging-fuzzers-with-gdb)
|
| 134 |
+
if needed.
|
| 135 |
+
- **Submit fix:** Submit the fix in the project's repository. ClusterFuzz will
|
| 136 |
+
automatically pick up the changes, recheck the testcase, and close the
|
| 137 |
+
issue (in < 1 day).
|
| 138 |
+
- **Improve fuzzing support:** Consider
|
| 139 |
+
[improving your integration with OSS-Fuzz]({{ site.baseurl }}/advanced-topics/ideal-integration/).
|
| 140 |
+
|
| 141 |
+
## Reproducing build failures
|
| 142 |
+
|
| 143 |
+
Our infrastructure runs some sanity tests to make sure that your build was
|
| 144 |
+
correctly configured, even if it succeeded. To reproduce these locally, run these commands:
|
| 145 |
+
|
| 146 |
+
```bash
|
| 147 |
+
$ python infra/helper.py build_image $PROJECT_NAME
|
| 148 |
+
$ python infra/helper.py build_fuzzers --sanitizer <address/memory/undefined> \
|
| 149 |
+
--engine <libfuzzer/afl/honggfuzz/centipede> --architecture <x86_64/i386> $PROJECT_NAME
|
| 150 |
+
$ python infra/helper.py check_build --sanitizer <address/memory/undefined> \
|
| 151 |
+
--engine <libfuzzer/afl/honggfuzz/centipede> --architecture <x86_64/i386> $PROJECT_NAME \
|
| 152 |
+
<fuzz_target_name>
|
| 153 |
+
```
|
| 154 |
+
|
| 155 |
+
**Note:** Unless you have a reason to think the build is an `i386` build, the build
|
| 156 |
+
is probably an `x86_64` build and the `architecture` argument can be omitted.
|
| 157 |
+
|
| 158 |
+
If you need to reproduce a `coverage` build failure, follow the
|
| 159 |
+
[Code Coverage page]({{ site.baseurl }}/advanced-topics/code-coverage) to build
|
| 160 |
+
your project and generate a code coverage report.
|
local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/assets/css/just-the-docs-wider.scss
ADDED
|
@@ -0,0 +1,3 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
---
|
| 3 |
+
{% include css/just-the-docs.scss.liquid color_scheme="wider" %}
|
local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/further-reading/clusterfuzz.md
ADDED
|
@@ -0,0 +1,67 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: ClusterFuzz
|
| 4 |
+
parent: Further reading
|
| 5 |
+
nav_order: 1
|
| 6 |
+
permalink: /further-reading/clusterfuzz/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# ClusterFuzz
|
| 10 |
+
|
| 11 |
+
[ClusterFuzz](https://github.com/google/clusterfuzz) is the distributed fuzzing
|
| 12 |
+
infrastructure behind OSS-Fuzz. It was initially built for fuzzing Chrome at
|
| 13 |
+
scale.
|
| 14 |
+
|
| 15 |
+
- TOC
|
| 16 |
+
{:toc}
|
| 17 |
+
---
|
| 18 |
+
|
| 19 |
+
## Web interface
|
| 20 |
+
|
| 21 |
+
ClusterFuzz provides a [web interface](https://oss-fuzz.com)
|
| 22 |
+
to view statistics about your fuzz targets, as well as current crashes.
|
| 23 |
+
|
| 24 |
+
*Note*: Access is restricted to project developers who we auto CC on new bug
|
| 25 |
+
reports.
|
| 26 |
+
|
| 27 |
+
## Testcase reports
|
| 28 |
+
|
| 29 |
+
ClusterFuzz will automatically de-duplicate and file reproducible crashes into
|
| 30 |
+
our [bug tracker](https://bugs.chromium.org/p/oss-fuzz/issues/list). We provide
|
| 31 |
+
a crash report page that gives you the stack trace, a link to the crashing
|
| 32 |
+
testcase, and regression ranges where the bug was most likely introduced.
|
| 33 |
+
|
| 34 |
+

|
| 35 |
+
|
| 36 |
+
## Fuzzer stats
|
| 37 |
+
|
| 38 |
+
You can view statistics about your fuzz targets (e.g. speed, coverage
|
| 39 |
+
information, memory usage) on our fuzzer statistics dashboard.
|
| 40 |
+
|
| 41 |
+

|
| 42 |
+
|
| 43 |
+

|
| 44 |
+
|
| 45 |
+
## Coverage reports
|
| 46 |
+
|
| 47 |
+
We provide coverage reports, where we highlight the parts of source code that
|
| 48 |
+
are being reached by your fuzz target. Make sure to look at the uncovered code
|
| 49 |
+
marked in red and add appropriate fuzz targets to cover those use cases.
|
| 50 |
+
|
| 51 |
+

|
| 52 |
+

|
| 53 |
+
|
| 54 |
+
## Performance analyzer
|
| 55 |
+
|
| 56 |
+
You can view performance issues that your fuzz target is running into (e.g.
|
| 57 |
+
leaks, timeouts, etc) by clicking on `Performance` link on our fuzzer statistics
|
| 58 |
+
dashboard. Make sure to fix all cited issues, so as to keep your fuzz target
|
| 59 |
+
running efficiently and finding new bugs.
|
| 60 |
+
|
| 61 |
+

|
| 62 |
+
|
| 63 |
+
## Crash stats
|
| 64 |
+
|
| 65 |
+
You can view statistics of crashes over time on our crash statistics dashboard.
|
| 66 |
+
|
| 67 |
+

|
local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/further-reading/further_reading.md
ADDED
|
@@ -0,0 +1,9 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Further reading
|
| 4 |
+
has_children: true
|
| 5 |
+
nav_order: 4
|
| 6 |
+
permalink: /further-reading/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Further reading
|
local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/further-reading/fuzzer_environment.md
ADDED
|
@@ -0,0 +1,77 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Fuzzer environment
|
| 4 |
+
parent: Further reading
|
| 5 |
+
nav_order: 2
|
| 6 |
+
permalink: /further-reading/fuzzer-environment/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Fuzzer environment on ClusterFuzz
|
| 10 |
+
|
| 11 |
+
Your fuzz targets will be run on a
|
| 12 |
+
[Google Compute Engine](https://cloud.google.com/compute/) VM (Linux).
|
| 13 |
+
|
| 14 |
+
- TOC
|
| 15 |
+
{:toc}
|
| 16 |
+
---
|
| 17 |
+
|
| 18 |
+
## Runtime Dependencies
|
| 19 |
+
|
| 20 |
+
You should not make any assumptions on the availability of dependent packages
|
| 21 |
+
in the execution environment. Packages that are installed via
|
| 22 |
+
[Dockerfile]({{ site.baseurl }}/getting-started/new-project-guide/#dockerfile)
|
| 23 |
+
or built as part of
|
| 24 |
+
[build.sh]({{ site.baseurl }}/getting-started/new-project-guide/#buildsh)
|
| 25 |
+
are not available on the bot runtime environment (where the fuzz targets run).
|
| 26 |
+
|
| 27 |
+
If you need these dependencies in the runtime environment, you can either:
|
| 28 |
+
- Install the packages via Dockerfile
|
| 29 |
+
([example](https://github.com/google/oss-fuzz/blob/2d5e2ef84f281e6ab789055aa735606d3122fda9/projects/tor/Dockerfile#L19))
|
| 30 |
+
and then link statically against them
|
| 31 |
+
([example](https://github.com/google/oss-fuzz/blob/2d5e2ef84f281e6ab789055aa735606d3122fda9/projects/tor/build.sh#L40)).
|
| 32 |
+
- Or build the dependencies statically in
|
| 33 |
+
[build.sh]({{ site.baseurl }}/getting-started/new-project-guide/#buildsh)
|
| 34 |
+
([example](https://github.com/google/oss-fuzz/blob/64f8b6593da141b97c98c7bc6f07df92c42ee010/projects/ffmpeg/build.sh#L26)).
|
| 35 |
+
|
| 36 |
+
All build artifacts needed during fuzz target execution should be inside the
|
| 37 |
+
`$OUT` directory. Only those artifacts are archived and used on the bots.
|
| 38 |
+
Everything else is ignored (e.g. artifacts in `$WORK`, `$SRC`, etc) and hence
|
| 39 |
+
is not available in the execution environment.
|
| 40 |
+
|
| 41 |
+
We strongly recommend static linking because it just works.
|
| 42 |
+
However dynamic linking can work if shared objects are included in the `$OUT` directory and are loaded relative
|
| 43 |
+
to `'$ORIGIN'`, the path of the binary (see the discussion of `'$ORIGIN'` [here](http://man7.org/linux/man-pages/man8/ld.so.8.html)).
|
| 44 |
+
A fuzzer can be instructed to load libraries relative to `'$ORIGIN'` during compilation (i.e. `-Wl,-rpath,'$ORIGIN/lib'` )
|
| 45 |
+
or afterwards using `chrpath -r '$ORIGIN/lib' $OUT/$fuzzerName` ([example](https://github.com/google/oss-fuzz/blob/09aa9ac556f97bd4e31928747eca0c8fed42509f/projects/php/build.sh#L40)). Note that `'$ORIGIN'` should be surrounded
|
| 46 |
+
by single quotes because it is not an environment variable like `$OUT` that can be retrieved during execution of `build.sh`.
|
| 47 |
+
Its value is retrieved during execution of the binary. You can verify that you did this correctly using `ldd <fuzz_target_name>` and the `check_build` command in `infra/helper.py`.
|
| 48 |
+
|
| 49 |
+
You should ensure that the fuzz target works correctly by using `run_fuzzer`
|
| 50 |
+
command (see instructions
|
| 51 |
+
[here]({{ site.baseurl }}/getting-started/new-project-guide/#testing-locally)).
|
| 52 |
+
This command uses a clean base-runner docker container and not the base-builder
|
| 53 |
+
docker container created during build-time.
|
| 54 |
+
|
| 55 |
+
## argv[0]
|
| 56 |
+
|
| 57 |
+
You must not modify `argv[0]`. It is required for certain things to work
|
| 58 |
+
correctly.
|
| 59 |
+
|
| 60 |
+
## Current working directory
|
| 61 |
+
|
| 62 |
+
You should not make any assumptions about the current working directory of your
|
| 63 |
+
fuzz target. If you need to load data files, please use `argv[0]` to get the
|
| 64 |
+
directory where your fuzz target executable is located.
|
| 65 |
+
|
| 66 |
+
## File system
|
| 67 |
+
|
| 68 |
+
Everything except `/tmp` is read-only, including the directory that your fuzz
|
| 69 |
+
target executable lives in.
|
| 70 |
+
|
| 71 |
+
`/dev` is also unavailable.
|
| 72 |
+
|
| 73 |
+
## Hardware
|
| 74 |
+
|
| 75 |
+
Your project should not be compiled with `-march=native` or `-mtune=native`
|
| 76 |
+
flags, as the build infrastructure and fuzzing machines may have different CPUs
|
| 77 |
+
as well as other hardware differences. You may however use `-mtune=generic`.
|
local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/getting-started/bug_disclosure_guidelines.md
ADDED
|
@@ -0,0 +1,23 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Bug disclosure guidelines
|
| 4 |
+
parent: Getting started
|
| 5 |
+
nav_order: 4
|
| 6 |
+
permalink: /getting-started/bug-disclosure-guidelines/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
## Bug Disclosure Guidelines
|
| 10 |
+
|
| 11 |
+
Following [Google's standard disclosure policy](https://googleprojectzero.blogspot.com/2015/02/feedback-and-data-driven-updates-to.html),
|
| 12 |
+
OSS-Fuzz will adhere to following disclosure principles:
|
| 13 |
+
|
| 14 |
+
- **Deadline**. After notifying project authors, we will open reported
|
| 15 |
+
issues to the public in 90 days, or after the fix is released (whichever
|
| 16 |
+
comes earlier).
|
| 17 |
+
- **Weekends and holidays**. If a deadline is due to expire on a weekend,
|
| 18 |
+
the deadline will be moved to the next normal work day.
|
| 19 |
+
- **Grace period**. We have a 14-day grace period. If a 90-day deadline
|
| 20 |
+
expires but the upstream engineers let us know before the deadline that a
|
| 21 |
+
patch is scheduled for release on a specific day within 14 days following
|
| 22 |
+
the deadline, the public disclosure will be delayed until the availability
|
| 23 |
+
of the patch.
|
local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/getting-started/continuous_integration.md
ADDED
|
@@ -0,0 +1,271 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Continuous Integration
|
| 4 |
+
parent: Getting started
|
| 5 |
+
nav_order: 5
|
| 6 |
+
permalink: /getting-started/continuous-integration/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Continuous Integration
|
| 10 |
+
|
| 11 |
+
OSS-Fuzz offers **CIFuzz**, a GitHub action/CI job that runs your fuzz targets
|
| 12 |
+
on pull requests. This works similarly to running unit tests in CI. CIFuzz helps
|
| 13 |
+
you find and fix bugs before they make it into your codebase.
|
| 14 |
+
Currently, CIFuzz primarily supports projects hosted on GitHub.
|
| 15 |
+
Non-OSS-Fuzz users can use CIFuzz with additional features through
|
| 16 |
+
[ClusterFuzzLite](https://google.github.io/clusterfuzzlite/).
|
| 17 |
+
|
| 18 |
+
## How it works
|
| 19 |
+
|
| 20 |
+
CIFuzz builds your project's fuzzers from the source at a particular
|
| 21 |
+
pull request or commit. Then CIFuzz runs the fuzzers for a short amount of time.
|
| 22 |
+
If CIFuzz finds a crash, CIFuzz reports the stacktrace, makes the crashing
|
| 23 |
+
input available for download and the CI test fails (red X).
|
| 24 |
+
|
| 25 |
+
If CIFuzz doesn't find a crash during the allotted time, the CI test passes
|
| 26 |
+
(green check). If CIFuzz finds a crash, it reports the crash only if both of
|
| 27 |
+
following are true:
|
| 28 |
+
* The crash is reproducible (on the PR/commit build).
|
| 29 |
+
* The crash does not occur on older OSS-Fuzz builds. (If the crash does occur
|
| 30 |
+
on older builds, then it was not introduced by the PR/commit
|
| 31 |
+
being tested.)
|
| 32 |
+
|
| 33 |
+
If your project supports [OSS-Fuzz's code coverage]({{ site.baseurl }}/advanced-topics/code-coverage),
|
| 34 |
+
CIFuzz only runs the fuzzers affected by a pull request/commit.
|
| 35 |
+
Otherwise it will divide up the allotted fuzzing time (10 minutes by default)
|
| 36 |
+
among all fuzzers in the project.
|
| 37 |
+
|
| 38 |
+
CIFuzz uses 30 day old/public regressions and corpora from OSS-Fuzz. This makes
|
| 39 |
+
fuzzing more effective and gives you regression testing for free.
|
| 40 |
+
|
| 41 |
+
## Requirements
|
| 42 |
+
|
| 43 |
+
1. Your project must be integrated with OSS-Fuzz.
|
| 44 |
+
1. Your project is hosted on GitHub.
|
| 45 |
+
1. Your repository needs to be cloned with `git` in oss-fuzz Dockerfile (do not use `go get` or other methods)
|
| 46 |
+
|
| 47 |
+
## Integrating into your repository
|
| 48 |
+
|
| 49 |
+
You can integrate CIFuzz into your project using the following steps:
|
| 50 |
+
1. Create a `.github` directory in the root of your project.
|
| 51 |
+
1. Create a `workflows` directory inside of your `.github` directory.
|
| 52 |
+
1. Copy the example [`cifuzz.yml`](https://github.com/google/oss-fuzz/blob/master/infra/cifuzz/example_cifuzz.yml)
|
| 53 |
+
file over from the OSS-Fuzz repository to the `workflows` directory.
|
| 54 |
+
1. Change the `oss-fuzz-project-name` value in `cifuzz.yml` from `example` to the name of your OSS-Fuzz project. It is **very important** that you use your OSS-Fuzz project name which is case sensitive. This name
|
| 55 |
+
is the name of your project's subdirectory in the [`projects`](https://github.com/google/oss-fuzz/tree/master/projects) directory of OSS-Fuzz.
|
| 56 |
+
1. Set the value of `fuzz-seconds`. The longest time that the project maintainers are acceptable with should be used. This value should be at minimum 600 seconds and scale with project size.
|
| 57 |
+
|
| 58 |
+
Your directory structure should look like the following:
|
| 59 |
+
```
|
| 60 |
+
project
|
| 61 |
+
|___ .github
|
| 62 |
+
| |____ workflows
|
| 63 |
+
| |____ cifuzz.yml
|
| 64 |
+
|___ other-files
|
| 65 |
+
```
|
| 66 |
+
|
| 67 |
+
cifuzz.yml for an example project:
|
| 68 |
+
|
| 69 |
+
```yaml
|
| 70 |
+
name: CIFuzz
|
| 71 |
+
on: [pull_request]
|
| 72 |
+
permissions: {}
|
| 73 |
+
jobs:
|
| 74 |
+
Fuzzing:
|
| 75 |
+
runs-on: ubuntu-latest
|
| 76 |
+
permissions:
|
| 77 |
+
security-events: write
|
| 78 |
+
steps:
|
| 79 |
+
- name: Build Fuzzers
|
| 80 |
+
id: build
|
| 81 |
+
uses: google/oss-fuzz/infra/cifuzz/actions/build_fuzzers@master
|
| 82 |
+
with:
|
| 83 |
+
oss-fuzz-project-name: 'example'
|
| 84 |
+
language: c++
|
| 85 |
+
- name: Run Fuzzers
|
| 86 |
+
uses: google/oss-fuzz/infra/cifuzz/actions/run_fuzzers@master
|
| 87 |
+
with:
|
| 88 |
+
oss-fuzz-project-name: 'example'
|
| 89 |
+
language: c++
|
| 90 |
+
fuzz-seconds: 600
|
| 91 |
+
output-sarif: true
|
| 92 |
+
- name: Upload Crash
|
| 93 |
+
uses: actions/upload-artifact@v3
|
| 94 |
+
if: failure() && steps.build.outcome == 'success'
|
| 95 |
+
with:
|
| 96 |
+
name: artifacts
|
| 97 |
+
path: ./out/artifacts
|
| 98 |
+
- name: Upload Sarif
|
| 99 |
+
if: always() && steps.build.outcome == 'success'
|
| 100 |
+
uses: github/codeql-action/upload-sarif@v2
|
| 101 |
+
with:
|
| 102 |
+
# Path to SARIF file relative to the root of the repository
|
| 103 |
+
sarif_file: cifuzz-sarif/results.sarif
|
| 104 |
+
checkout_path: cifuzz-sarif
|
| 105 |
+
```
|
| 106 |
+
|
| 107 |
+
|
| 108 |
+
### Optional configuration
|
| 109 |
+
|
| 110 |
+
#### Configurable Variables
|
| 111 |
+
|
| 112 |
+
`language`: (optional) The language your target program is written in. Defaults
|
| 113 |
+
to `c++`. This should be the same as the value you set in `project.yaml`. See
|
| 114 |
+
[this explanation]({{ site.baseurl }}//getting-started/new-project-guide/#language)
|
| 115 |
+
for more details.
|
| 116 |
+
|
| 117 |
+
`fuzz-seconds`: Determines how long CIFuzz spends fuzzing your project in seconds.
|
| 118 |
+
The default is 600 seconds. The GitHub Actions max run time is 21600 seconds (6
|
| 119 |
+
hours). This variable is only meaningful when supplied to the `run_fuzzers`
|
| 120 |
+
action, not the `build_fuzzers` action.
|
| 121 |
+
|
| 122 |
+
`dry-run`: Determines if CIFuzz surfaces errors. The default value is `false`. When set to `true`,
|
| 123 |
+
CIFuzz will never report a failure even if it finds a crash in your project.
|
| 124 |
+
This requires the user to manually check the logs for detected bugs. If dry run mode is desired,
|
| 125 |
+
make sure to set the dry-run parameters in both the `Build Fuzzers` and `Run Fuzzers` action step.
|
| 126 |
+
|
| 127 |
+
`allowed-broken-targets-percentage`: Can be set if you want to set a stricter
|
| 128 |
+
limit for broken fuzz targets than OSS-Fuzz's check_build. Most users should
|
| 129 |
+
not set this. This value is only meaningful when supplied to the `run_fuzzers`
|
| 130 |
+
action, not the `build_fuzzers` action.
|
| 131 |
+
|
| 132 |
+
`sanitizer`: Determines a sanitizer to build and run fuzz targets with. The choices are `'address'`,
|
| 133 |
+
`'memory'` and `'undefined'`. The default is `'address'`. It is important to note that the `Build Fuzzers`
|
| 134 |
+
and the `Run Fuzzers` sanitizer field needs to be the same. To specify a list of sanitizers
|
| 135 |
+
a [matrix](https://help.github.com/en/actions/reference/workflow-syntax-for-github-actions#jobsjob_idstrategymatrix)
|
| 136 |
+
can be used. To use a sanitizer add it to the list of sanitizers in the matrix field below:
|
| 137 |
+
|
| 138 |
+
`report-timeouts`: Determines whether to report fails due to timeouts.
|
| 139 |
+
|
| 140 |
+
`report-ooms`: Determines whether to report fails due to OOM.
|
| 141 |
+
|
| 142 |
+
```yaml
|
| 143 |
+
{% raw %}
|
| 144 |
+
name: CIFuzz
|
| 145 |
+
on: [pull_request]
|
| 146 |
+
permissions: {}
|
| 147 |
+
jobs:
|
| 148 |
+
Fuzzing:
|
| 149 |
+
runs-on: ubuntu-latest
|
| 150 |
+
permissions:
|
| 151 |
+
security-events: write
|
| 152 |
+
strategy:
|
| 153 |
+
fail-fast: false
|
| 154 |
+
matrix:
|
| 155 |
+
sanitizer: [address, undefined, memory]
|
| 156 |
+
steps:
|
| 157 |
+
- name: Build Fuzzers (${{ matrix.sanitizer }})
|
| 158 |
+
id: build
|
| 159 |
+
uses: google/oss-fuzz/infra/cifuzz/actions/build_fuzzers@master
|
| 160 |
+
with:
|
| 161 |
+
oss-fuzz-project-name: 'example'
|
| 162 |
+
language: c++
|
| 163 |
+
sanitizer: ${{ matrix.sanitizer }}
|
| 164 |
+
- name: Run Fuzzers (${{ matrix.sanitizer }})
|
| 165 |
+
uses: google/oss-fuzz/infra/cifuzz/actions/run_fuzzers@master
|
| 166 |
+
with:
|
| 167 |
+
oss-fuzz-project-name: 'example'
|
| 168 |
+
language: c++
|
| 169 |
+
fuzz-seconds: 600
|
| 170 |
+
sanitizer: ${{ matrix.sanitizer }}
|
| 171 |
+
output-sarif: true
|
| 172 |
+
- name: Upload Crash
|
| 173 |
+
uses: actions/upload-artifact@v3
|
| 174 |
+
if: steps.build.outcome == 'success'
|
| 175 |
+
with:
|
| 176 |
+
name: ${{ matrix.sanitizer }}-artifacts
|
| 177 |
+
path: ./out/artifacts
|
| 178 |
+
- name: Upload Sarif
|
| 179 |
+
if: always() && steps.build.outcome == 'success'
|
| 180 |
+
uses: github/codeql-action/upload-sarif@v2
|
| 181 |
+
with:
|
| 182 |
+
# Path to SARIF file relative to the root of the repository
|
| 183 |
+
sarif_file: cifuzz-sarif/results.sarif
|
| 184 |
+
checkout_path: cifuzz-sarif
|
| 185 |
+
{% endraw %}
|
| 186 |
+
```
|
| 187 |
+
|
| 188 |
+
#### Branches and paths
|
| 189 |
+
|
| 190 |
+
You can make CIFuzz trigger only on certain branches or paths by following the
|
| 191 |
+
instructions [here](https://docs.github.com/en/actions/reference/workflow-syntax-for-github-actions).
|
| 192 |
+
For example, the following code can used to trigger CIFuzz only on changes to
|
| 193 |
+
C/C++ code residing on master and release branches:
|
| 194 |
+
|
| 195 |
+
```yaml
|
| 196 |
+
name: CIFuzz
|
| 197 |
+
on:
|
| 198 |
+
pull_request:
|
| 199 |
+
branches:
|
| 200 |
+
- master
|
| 201 |
+
- 'releases/**'
|
| 202 |
+
paths:
|
| 203 |
+
- '**.c'
|
| 204 |
+
- '**.cc'
|
| 205 |
+
- '**.cpp'
|
| 206 |
+
- '**.cxx'
|
| 207 |
+
- '**.h'
|
| 208 |
+
permissions: {}
|
| 209 |
+
jobs:
|
| 210 |
+
Fuzzing:
|
| 211 |
+
runs-on: ubuntu-latest
|
| 212 |
+
steps:
|
| 213 |
+
- name: Build Fuzzers
|
| 214 |
+
id: build
|
| 215 |
+
uses: google/oss-fuzz/infra/cifuzz/actions/build_fuzzers@master
|
| 216 |
+
with:
|
| 217 |
+
oss-fuzz-project-name: 'example'
|
| 218 |
+
language: c++
|
| 219 |
+
- name: Run Fuzzers
|
| 220 |
+
uses: google/oss-fuzz/infra/cifuzz/actions/run_fuzzers@master
|
| 221 |
+
with:
|
| 222 |
+
oss-fuzz-project-name: 'example'
|
| 223 |
+
language: c++
|
| 224 |
+
fuzz-seconds: 600
|
| 225 |
+
- name: Upload Crash
|
| 226 |
+
uses: actions/upload-artifact@v3
|
| 227 |
+
if: failure() && steps.build.outcome == 'success'
|
| 228 |
+
with:
|
| 229 |
+
name: artifacts
|
| 230 |
+
path: ./out/artifacts
|
| 231 |
+
```
|
| 232 |
+
|
| 233 |
+
You can checkout CIFuzz configs for OSS-Fuzz projects. Example -
|
| 234 |
+
[systemd](https://github.com/systemd/systemd/blob/main/.github/workflows/cifuzz.yml),
|
| 235 |
+
[curl](https://github.com/curl/curl/blob/master/.github/workflows/fuzz.yml).
|
| 236 |
+
|
| 237 |
+
## Understanding results
|
| 238 |
+
|
| 239 |
+
The results of CIFuzz can be found in two different places.
|
| 240 |
+
|
| 241 |
+
* Run fuzzers log:
|
| 242 |
+
1. This log can be accessed in the `actions` tab of a CIFuzz integrated repo.
|
| 243 |
+
1. Click on the `CIFuzz` button in the workflow selector on the left hand side.
|
| 244 |
+
1. Click on the event triggered by your desired pull request.
|
| 245 |
+
1. Click the `Fuzzing` workflow.
|
| 246 |
+
1. Select the `Run Fuzzer` drop down. It should show the timestamps and results
|
| 247 |
+
from each of the fuzz targets.
|
| 248 |
+
|
| 249 |
+

|
| 250 |
+
|
| 251 |
+
|
| 252 |
+
|
| 253 |
+
* Artifacts:
|
| 254 |
+
When the fuzzer crashes the input file that causes the crash is uploaded as an
|
| 255 |
+
artifact.
|
| 256 |
+
To download the artifact, do the following steps:
|
| 257 |
+
1. Click on the summary from the run, as illustrated in the screenshot below:
|
| 258 |
+
|
| 259 |
+
![github-actions-summary]
|
| 260 |
+
|
| 261 |
+
2. Click on the artifact you wish to download from the summary page, as
|
| 262 |
+
illustrated in the screenshot below:
|
| 263 |
+
|
| 264 |
+
![github-actions-download-crash]
|
| 265 |
+
|
| 266 |
+
[github-actions-summary]: (https://raw.githubusercontent.com/google/clusterfuzzlite/refs/heads/bucket/images/github-actions-summary.png)
|
| 267 |
+
[github-actions-download-crash]: (https://raw.githubusercontent.com/google/clusterfuzzlite/refs/heads/bucket/images/github-actions-download-crash.png)
|
| 268 |
+
|
| 269 |
+
## Feedback/Questions/Issues
|
| 270 |
+
|
| 271 |
+
Create an issue in [OSS-Fuzz](https://github.com/google/oss-fuzz/issues/new) if you have questions or any other feedback on CIFuzz.
|
local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/getting-started/getting_started.md
ADDED
|
@@ -0,0 +1,11 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Getting started
|
| 4 |
+
has_children: true
|
| 5 |
+
nav_order: 2
|
| 6 |
+
permalink: /getting-started/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Getting started
|
| 10 |
+
These pages walk you through the process of integrating your open source project
|
| 11 |
+
with OSS-Fuzz.
|
local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/getting-started/new-project-guide/rust_lang.md
ADDED
|
@@ -0,0 +1,148 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Integrating a Rust project
|
| 4 |
+
parent: Setting up a new project
|
| 5 |
+
grand_parent: Getting started
|
| 6 |
+
nav_order: 2
|
| 7 |
+
permalink: /getting-started/new-project-guide/rust-lang/
|
| 8 |
+
---
|
| 9 |
+
|
| 10 |
+
# Integrating a Rust project
|
| 11 |
+
{: .no_toc}
|
| 12 |
+
|
| 13 |
+
- TOC
|
| 14 |
+
{:toc}
|
| 15 |
+
---
|
| 16 |
+
|
| 17 |
+
The process of integrating a project written in Rust with OSS-Fuzz is very
|
| 18 |
+
similar to the general [Setting up a new project]({{ site.baseurl
|
| 19 |
+
}}/getting-started/new-project-guide/) process. The key specifics of integrating
|
| 20 |
+
a Rust project are outlined below.
|
| 21 |
+
|
| 22 |
+
## cargo-fuzz support
|
| 23 |
+
|
| 24 |
+
Rust integration with OSS-Fuzz is expected to use [`cargo
|
| 25 |
+
fuzz`](https://github.com/rust-fuzz/cargo-fuzz) to build fuzzers. The `cargo
|
| 26 |
+
fuzz` tool will build code with required compiler flags as well as link to the
|
| 27 |
+
correct libFuzzer on OSS-Fuzz itself. Note that using `cargo fuzz` also makes it
|
| 28 |
+
quite easy to run the fuzzers locally yourself if you get a failing test case!
|
| 29 |
+
|
| 30 |
+
## Project files
|
| 31 |
+
|
| 32 |
+
First you'll want to follow the [setup instructions for `cargo fuzz`
|
| 33 |
+
itself](https://rust-fuzz.github.io/book/). Afterwards your project should have:
|
| 34 |
+
|
| 35 |
+
* A top-level `fuzz` directory.
|
| 36 |
+
* A `fuzz/Cargo.toml` manifest which pulls in necessary dependencies to fuzz.
|
| 37 |
+
* Some `fuzz/fuzz_targets/*.rs` files which are the fuzz targets that will be
|
| 38 |
+
compiled and run on OSS-Fuzz.
|
| 39 |
+
|
| 40 |
+
Note that you can customize this layout as well, but you'll need to edit some
|
| 41 |
+
the scripts below to integrate into OSS-Fuzz.
|
| 42 |
+
|
| 43 |
+
### project.yaml
|
| 44 |
+
|
| 45 |
+
The `language` attribute must be specified.
|
| 46 |
+
|
| 47 |
+
```yaml
|
| 48 |
+
language: rust
|
| 49 |
+
```
|
| 50 |
+
|
| 51 |
+
The only supported fuzzing engine and sanitizer are `libfuzzer` and `address`,
|
| 52 |
+
respectively.
|
| 53 |
+
[Example](https://github.com/google/oss-fuzz/blob/12ef3654b3e9adfd20b5a6afdde54819ba71493d/projects/serde_json/project.yaml#L3-L6)
|
| 54 |
+
|
| 55 |
+
```yaml
|
| 56 |
+
sanitizers:
|
| 57 |
+
- address
|
| 58 |
+
fuzzing_engines:
|
| 59 |
+
- libfuzzer
|
| 60 |
+
```
|
| 61 |
+
|
| 62 |
+
### Dockerfile
|
| 63 |
+
|
| 64 |
+
The Dockerfile should start by `FROM gcr.io/oss-fuzz-base/base-builder-rust`
|
| 65 |
+
|
| 66 |
+
The OSS-Fuzz builder image has the latest nightly release of Rust as well as
|
| 67 |
+
`cargo fuzz` pre-installed and in `PATH`. In the `Dockerfile` for your project
|
| 68 |
+
all you'll need to do is fetch the latest copy of your code and install any
|
| 69 |
+
system dependencies necessary to build your project.
|
| 70 |
+
[Example](https://github.com/google/oss-fuzz/blob/12ef3654b3e9adfd20b5a6afdde54819ba71493d/projects/serde_json/Dockerfile#L18-L20)
|
| 71 |
+
|
| 72 |
+
```dockerfile
|
| 73 |
+
RUN git clone --depth 1 https://github.com/serde-rs/json json
|
| 74 |
+
```
|
| 75 |
+
|
| 76 |
+
### build.sh
|
| 77 |
+
|
| 78 |
+
Here it's expected that you'll build the fuzz targets for your project and then
|
| 79 |
+
copy the final binaries into the output directory.
|
| 80 |
+
[Example](https://github.com/google/oss-fuzz/blob/12ef3654b3e9adfd20b5a6afdde54819ba71493d/projects/serde_json/build.sh#L20):
|
| 81 |
+
|
| 82 |
+
```sh
|
| 83 |
+
cd $SRC/json
|
| 84 |
+
cargo fuzz build -O
|
| 85 |
+
cp fuzz/target/x86_64-unknown-linux-gnu/release/from_slice $OUT/
|
| 86 |
+
```
|
| 87 |
+
|
| 88 |
+
Note that you likely want to pass the `-O` flag to `cargo fuzz build` which
|
| 89 |
+
builds fuzzers in release mode. You may also want to pass the
|
| 90 |
+
`--debug-assertions` flag to enable more checks while fuzzing. In this example
|
| 91 |
+
the `from_slice` binary is the fuzz target.
|
| 92 |
+
|
| 93 |
+
With some bash-fu you can also automatically copy over all fuzz targets into
|
| 94 |
+
the output directory so when you add a fuzz target to your project it's
|
| 95 |
+
automatically integrated into OSS-Fuzz:
|
| 96 |
+
|
| 97 |
+
```sh
|
| 98 |
+
FUZZ_TARGET_OUTPUT_DIR=target/x86_64-unknown-linux-gnu/release
|
| 99 |
+
for f in fuzz/fuzz_targets/*.rs
|
| 100 |
+
do
|
| 101 |
+
FUZZ_TARGET_NAME=$(basename ${f%.*})
|
| 102 |
+
cp $FUZZ_TARGET_OUTPUT_DIR/$FUZZ_TARGET_NAME $OUT/
|
| 103 |
+
done
|
| 104 |
+
```
|
| 105 |
+
|
| 106 |
+
## Writing fuzzers using a test-style strategy
|
| 107 |
+
|
| 108 |
+
In Rust you will often have tests written in a way so they are only
|
| 109 |
+
compiled into the final binary when build in test-mode. This is, achieved by
|
| 110 |
+
wrapping your test code in `cfg(test)`, e.g.
|
| 111 |
+
```rust
|
| 112 |
+
#[cfg(test)]
|
| 113 |
+
mod tests {
|
| 114 |
+
use super::*;
|
| 115 |
+
|
| 116 |
+
...
|
| 117 |
+
```
|
| 118 |
+
|
| 119 |
+
Cargo-fuzz automatically enables the `fuzzing` feature, which means you can
|
| 120 |
+
follow a similar strategy to writing fuzzers as you do when writing tests.
|
| 121 |
+
Specifically, you can create modules wrapped in the `fuzzing` feature:
|
| 122 |
+
```rust
|
| 123 |
+
#[cfg(fuzzing)]
|
| 124 |
+
pub mod fuzz_logic {
|
| 125 |
+
use super::*;
|
| 126 |
+
|
| 127 |
+
...
|
| 128 |
+
```
|
| 129 |
+
and then call the logic within `fuzz_logic` from your fuzzer.
|
| 130 |
+
|
| 131 |
+
Furthermore, within your `.toml` files, you can then specify fuzzing-specific
|
| 132 |
+
dependencies by wrapping them as follows:
|
| 133 |
+
```
|
| 134 |
+
[target.'cfg(fuzzing)'.dependencies]
|
| 135 |
+
```
|
| 136 |
+
similar to how you wrap test-dependencies as follows:
|
| 137 |
+
```
|
| 138 |
+
[dev-dependencies]
|
| 139 |
+
```
|
| 140 |
+
|
| 141 |
+
Finally, you can also combine the testing logic you have and the fuzz logic. This
|
| 142 |
+
can be achieved simply by using
|
| 143 |
+
```rust
|
| 144 |
+
#[cfg(any(test, fuzzing))]
|
| 145 |
+
```
|
| 146 |
+
|
| 147 |
+
A project that follows this structure is Linkerd2-proxy and the project files can be
|
| 148 |
+
seen [here](https://github.com/google/oss-fuzz/tree/master/projects/linkerd2-proxy).
|
local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/getting-started/new_project_guide.md
ADDED
|
@@ -0,0 +1,553 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Setting up a new project
|
| 4 |
+
parent: Getting started
|
| 5 |
+
has_children: true
|
| 6 |
+
nav_order: 2
|
| 7 |
+
permalink: /getting-started/new-project-guide/
|
| 8 |
+
---
|
| 9 |
+
|
| 10 |
+
# Setting up a new project
|
| 11 |
+
{: .no_toc}
|
| 12 |
+
|
| 13 |
+
- TOC
|
| 14 |
+
{:toc}
|
| 15 |
+
---
|
| 16 |
+
|
| 17 |
+
## Prerequisites
|
| 18 |
+
|
| 19 |
+
Before you can start setting up your new project for fuzzing, you must do the following:
|
| 20 |
+
|
| 21 |
+
- [Integrate]({{ site.baseurl }}/advanced-topics/ideal-integration/) one or more [fuzz targets]({{ site.baseurl }}/reference/glossary/#fuzz-target)
|
| 22 |
+
with the project you want to fuzz.
|
| 23 |
+
|
| 24 |
+
For examples, see
|
| 25 |
+
[boringssl](https://github.com/google/boringssl/tree/master/fuzz) or
|
| 26 |
+
[SQLite](https://www.sqlite.org/src/artifact/ad79e867fb504338) (C/C++),
|
| 27 |
+
[go-fuzz](https://github.com/dvyukov/go-fuzz-corpus/tree/86a5af9d6842f80b205a082538ea28f61bbb8ccb) or
|
| 28 |
+
[syzkaller](https://github.com/google/syzkaller/tree/7c7ded697e6322b0975f061b7e268fe44f585dab/prog/test)
|
| 29 |
+
(Go).
|
| 30 |
+
|
| 31 |
+
- [Install Docker](https://docs.docker.com/engine/installation)
|
| 32 |
+
(Googlers can visit [go/installdocker](https://goto.google.com/installdocker)).
|
| 33 |
+
[Why Docker?]({{ site.baseurl }}/faq/#why-do-you-use-docker)
|
| 34 |
+
|
| 35 |
+
If you want to run `docker` without `sudo`, you can
|
| 36 |
+
[create a docker group](https://docs.docker.com/engine/installation/linux/ubuntulinux/#/create-a-docker-group).
|
| 37 |
+
|
| 38 |
+
**Note:** Docker images can consume significant disk space. Run
|
| 39 |
+
[docker-cleanup](https://gist.github.com/mikea/d23a839cba68778d94e0302e8a2c200f)
|
| 40 |
+
periodically to garbage-collect unused images.
|
| 41 |
+
|
| 42 |
+
- (optional) [Install gsutil](https://cloud.google.com/storage/docs/gsutil_install) for local code coverage testing.
|
| 43 |
+
For Google internal (gLinux) machines, please refer [here](https://cloud.google.com/storage/docs/gsutil_install#deb) instead.
|
| 44 |
+
|
| 45 |
+
## Creating the file structure
|
| 46 |
+
|
| 47 |
+
Each OSS-Fuzz project has a subdirectory
|
| 48 |
+
inside the [`projects/`](https://github.com/google/oss-fuzz/tree/master/projects) directory in the [OSS-Fuzz repository](https://github.com/google/oss-fuzz). For example, the [boringssl](https://github.com/google/boringssl)
|
| 49 |
+
project is located in [`projects/boringssl`](https://github.com/google/oss-fuzz/tree/master/projects/boringssl).
|
| 50 |
+
|
| 51 |
+
Each project directory also contains the following three configuration files:
|
| 52 |
+
|
| 53 |
+
* [project.yaml](#projectyaml) - provides metadata about the project.
|
| 54 |
+
* [Dockerfile](#dockerfile) - defines the container environment with information
|
| 55 |
+
on dependencies needed to build the project and its [fuzz targets]({{ site.baseurl }}/reference/glossary/#fuzz-target).
|
| 56 |
+
* [build.sh](#buildsh) - defines the build script that executes inside the Docker container and
|
| 57 |
+
generates the project build.
|
| 58 |
+
|
| 59 |
+
You can automatically create a new directory for your project in OSS-Fuzz and
|
| 60 |
+
generate templated versions of the configuration files
|
| 61 |
+
by running the following commands:
|
| 62 |
+
|
| 63 |
+
```bash
|
| 64 |
+
$ cd /path/to/oss-fuzz
|
| 65 |
+
$ export PROJECT_NAME=<project_name>
|
| 66 |
+
$ export LANGUAGE=<project_language>
|
| 67 |
+
$ python infra/helper.py generate $PROJECT_NAME --language=$LANGUAGE
|
| 68 |
+
```
|
| 69 |
+
|
| 70 |
+
Once the template configuration files are created, you can modify them to fit your project.
|
| 71 |
+
|
| 72 |
+
**Note:** We prefer that you keep and maintain [fuzz targets]({{ site.baseurl }}/reference/glossary/#fuzz-target) in your own source code repository. If this isn't possible, you can store them inside the OSS-Fuzz project directory you created.
|
| 73 |
+
|
| 74 |
+
## project.yaml {#projectyaml}
|
| 75 |
+
|
| 76 |
+
This configuration file stores project metadata. The following attributes are supported:
|
| 77 |
+
|
| 78 |
+
- [homepage](#homepage)
|
| 79 |
+
- [language](#language)
|
| 80 |
+
- [primary_contact](#primary)
|
| 81 |
+
- [auto_ccs](#auto_ccs)
|
| 82 |
+
- [main_repo](#main_repo)
|
| 83 |
+
- [vendor_ccs](#vendor) (optional)
|
| 84 |
+
- [sanitizers](#sanitizers) (optional)
|
| 85 |
+
- [architectures](#architectures) (optional)
|
| 86 |
+
- [help_url](#help_url) (optional)
|
| 87 |
+
- [builds_per_day](#build_frequency) (optional)
|
| 88 |
+
- [file_github_issue](#file_github_issue) (optional)
|
| 89 |
+
|
| 90 |
+
### homepage
|
| 91 |
+
You project's homepage.
|
| 92 |
+
|
| 93 |
+
### language
|
| 94 |
+
|
| 95 |
+
Programming language the project is written in. Values you can specify include:
|
| 96 |
+
|
| 97 |
+
* `c`
|
| 98 |
+
* `c++`
|
| 99 |
+
* [`go`]({{ site.baseurl }}//getting-started/new-project-guide/go-lang/)
|
| 100 |
+
* [`rust`]({{ site.baseurl }}//getting-started/new-project-guide/rust-lang/)
|
| 101 |
+
* [`python`]({{ site.baseurl }}//getting-started/new-project-guide/python-lang/)
|
| 102 |
+
* [`jvm` (Java, Kotlin, Scala and other JVM-based languages)]({{ site.baseurl }}//getting-started/new-project-guide/jvm-lang/)
|
| 103 |
+
* [`swift`]({{ site.baseurl }}//getting-started/new-project-guide/swift-lang/)
|
| 104 |
+
* [`javascript`]({{ site.baseurl }}//getting-started/new-project-guide/javascript-lang/)
|
| 105 |
+
|
| 106 |
+
### primary_contact, auto_ccs {#primary}
|
| 107 |
+
The primary contact and list of other contacts to be CCed. Each person listed gets access to ClusterFuzz, including crash reports and fuzzer statistics, and are auto-cced on new bugs filed in the OSS-Fuzz
|
| 108 |
+
tracker. If you're a primary or a CC, you'll need to use a [Google account](https://support.google.com/accounts/answer/176347?hl=en) to get full access. ([why?]({{ site.baseurl }}/faq/#why-do-you-require-a-google-account-for-authentication)).
|
| 109 |
+
|
| 110 |
+
### main_repo {#main_repo}
|
| 111 |
+
Path to source code repository hosting the code, e.g. `https://path/to/main/repo.git`.
|
| 112 |
+
|
| 113 |
+
### vendor_ccs (optional) {#vendor}
|
| 114 |
+
The list of vendor email addresses that are downstream consumers of the project and want access to
|
| 115 |
+
the bug reports as they are filed.
|
| 116 |
+
|
| 117 |
+
Any changes to this list must follow these rules:
|
| 118 |
+
- Approved by the project maintainer (e.g. comment on pull request, reply on project mailing list).
|
| 119 |
+
- An organization email address is used.
|
| 120 |
+
|
| 121 |
+
### sanitizers (optional) {#sanitizers}
|
| 122 |
+
The list of sanitizers to use. Possible values are: `address`, `memory` and `undefined`.
|
| 123 |
+
If you don't specify a list, `sanitizers` uses a default list of supported
|
| 124 |
+
sanitizers (currently ["address"](https://clang.llvm.org/docs/AddressSanitizer.html) and
|
| 125 |
+
["undefined"](https://clang.llvm.org/docs/UndefinedBehaviorSanitizer.html)).
|
| 126 |
+
|
| 127 |
+
[MemorySanitizer](https://clang.llvm.org/docs/MemorySanitizer.html) ("memory") is also supported
|
| 128 |
+
and recommended, but is not enabled by default due to the likelihood of false positives from
|
| 129 |
+
un-instrumented system dependencies.
|
| 130 |
+
If you want to use "memory," please build all libraries your project needs using
|
| 131 |
+
MemorySanitizer.
|
| 132 |
+
This can be done by building them with the compiler flags provided during
|
| 133 |
+
MemorySanitizer builds.
|
| 134 |
+
Then, you can opt in by adding "memory" to your list of sanitizers.
|
| 135 |
+
|
| 136 |
+
If your project does not build with a particular sanitizer configuration and you need some time to fix
|
| 137 |
+
it, you can use `sanitizers` to override the defaults temporarily. For example, to disable the
|
| 138 |
+
UndefinedBehaviourSanitizer build, just specify all supported sanitizers except "undefined".
|
| 139 |
+
|
| 140 |
+
If you want to test a particular sanitizer to see what crashes it generates without filing
|
| 141 |
+
them in the issue tracker, you can set an `experimental` flag. For example, if you want to test "memory", set `experimental: True` like this:
|
| 142 |
+
|
| 143 |
+
```
|
| 144 |
+
sanitizers:
|
| 145 |
+
- address
|
| 146 |
+
- memory:
|
| 147 |
+
experimental: True
|
| 148 |
+
- undefined
|
| 149 |
+
```
|
| 150 |
+
|
| 151 |
+
Crashes can be accessed on the [ClusterFuzz
|
| 152 |
+
homepage]({{ site.baseurl }}/further-reading/clusterfuzz#web-interface).
|
| 153 |
+
|
| 154 |
+
`sanitizers` example: [boringssl](https://github.com/google/oss-fuzz/blob/master/projects/boringssl/project.yaml).
|
| 155 |
+
|
| 156 |
+
### architectures (optional) {#architectures}
|
| 157 |
+
The list of architectures to fuzz on.
|
| 158 |
+
ClusterFuzz supports fuzzing on x86_64 (aka x64) by default.
|
| 159 |
+
Some projects can benefit from i386 fuzzing. OSS-Fuzz will build and run
|
| 160 |
+
AddressSanitizer with libFuzzer on i386 by doing the following:
|
| 161 |
+
|
| 162 |
+
```yaml
|
| 163 |
+
architectures:
|
| 164 |
+
- x86_64
|
| 165 |
+
- i386
|
| 166 |
+
```
|
| 167 |
+
|
| 168 |
+
By fuzzing on i386 you might find bugs that:
|
| 169 |
+
* Only occur in architecture-specific source code (e.g. code that contains i386 assembly).
|
| 170 |
+
* Exist in architecture-independent source code and which only affects i386 users.
|
| 171 |
+
* Exist in architecture-independent source code and which affects users on other 32-bit platforms such as AArch32 (aka 32-bit ARM).
|
| 172 |
+
|
| 173 |
+
Note that some bugs which affect x86_64 may be discovered on i386 and filed as such.
|
| 174 |
+
On the testcase page of each oss-fuzz issue is a list of other jobs where the crash reproduces, this can let you know if the crash exists on x86_64 as well.
|
| 175 |
+
|
| 176 |
+
Fuzzing on i386 is not enabled by default because many projects won't build for i386 without some modification to their OSS-Fuzz build process.
|
| 177 |
+
For example, you will need to link against `$LIB_FUZZING_ENGINE` and possibly install i386 dependencies within the x86_64 docker image ([for example](https://github.com/google/oss-fuzz/blob/5b8dcb5d942b3b8bc173b823fb9ddbdca7ec6c99/projects/gdal/build.sh#L18)) to get things working.
|
| 178 |
+
|
| 179 |
+
There are [known bugs](https://github.com/google/oss-fuzz/issues/2746) in ASAN
|
| 180 |
+
on i386 that cause ClusterFuzz to report unreproducible crashes for 0 length
|
| 181 |
+
testcases. There are no plans to fix these bugs so be ready for slightly more
|
| 182 |
+
false positives if you use i386. These false positives should be somewhat easy
|
| 183 |
+
to identify since they will manifest as crashes in ASAN rather than your code.
|
| 184 |
+
|
| 185 |
+
### fuzzing_engines (optional) {#fuzzing_engines}
|
| 186 |
+
The list of fuzzing engines to use.
|
| 187 |
+
By default, `libfuzzer`, `afl`, `honggfuzz`, and `centipede` are used. It is recommended to
|
| 188 |
+
use all of them if possible. `libfuzzer` is required by OSS-Fuzz.
|
| 189 |
+
|
| 190 |
+
### help_url (optional) {#help_url}
|
| 191 |
+
A link to a custom help URL that appears in bug reports instead of the default
|
| 192 |
+
[OSS-Fuzz guide to reproducing crashes]({{ site.baseurl }}/advanced-topics/reproducing/). This can be useful if you assign
|
| 193 |
+
bugs to members of your project unfamiliar with OSS-Fuzz, or if they should follow a different workflow for
|
| 194 |
+
reproducing and fixing bugs than the standard one outlined in the reproducing guide.
|
| 195 |
+
|
| 196 |
+
`help_url` example: [skia](https://github.com/google/oss-fuzz/blob/master/projects/skia/project.yaml).
|
| 197 |
+
|
| 198 |
+
### builds_per_day (optional) {#build_frequency}
|
| 199 |
+
The number of times the project should be built per day.
|
| 200 |
+
OSS-Fuzz allows upto 4 builds per day, and builds once per day by default.
|
| 201 |
+
Example:
|
| 202 |
+
```yaml
|
| 203 |
+
builds_per_day: 2
|
| 204 |
+
```
|
| 205 |
+
|
| 206 |
+
Will build the project twice per day.
|
| 207 |
+
|
| 208 |
+
### file_github_issue (optional) {#file_github_issue}
|
| 209 |
+
Whether to mirror issues on github instead of having them only in the OSS-Fuzz
|
| 210 |
+
tracker.
|
| 211 |
+
|
| 212 |
+
## Dockerfile {#dockerfile}
|
| 213 |
+
|
| 214 |
+
This configuration file defines the Docker image for your project. Your [build.sh](#buildsh) script will be executed in inside the container you define.
|
| 215 |
+
For most projects, the image is simple:
|
| 216 |
+
```docker
|
| 217 |
+
FROM gcr.io/oss-fuzz-base/base-builder # base image with clang toolchain
|
| 218 |
+
RUN apt-get update && apt-get install -y ... # install required packages to build your project
|
| 219 |
+
RUN git clone <git_url> <checkout_dir> # checkout all sources needed to build your project
|
| 220 |
+
WORKDIR <checkout_dir> # current directory for the build script
|
| 221 |
+
COPY build.sh fuzzer.cc $SRC/ # copy build script and other fuzzer files in src dir
|
| 222 |
+
```
|
| 223 |
+
In the above example, the git clone will check out the source to `$SRC/<checkout_dir>`.
|
| 224 |
+
|
| 225 |
+
Depending on your project's language, you will use a different base image,
|
| 226 |
+
for instance `FROM gcr.io/oss-fuzz-base/base-builder-go` for golang.
|
| 227 |
+
|
| 228 |
+
For an example, see
|
| 229 |
+
[expat/Dockerfile](https://github.com/google/oss-fuzz/tree/master/projects/expat/Dockerfile)
|
| 230 |
+
or
|
| 231 |
+
[syzkaller/Dockerfile](https://github.com/google/oss-fuzz/blob/master/projects/syzkaller/Dockerfile).
|
| 232 |
+
|
| 233 |
+
In the case of a project with multiple languages/toolchains needed,
|
| 234 |
+
you can run installation scripts `install_lang.sh` where lang is the language needed.
|
| 235 |
+
You also need to setup environment variables needed by this toolchain, for example `GOPATH` is needed by golang.
|
| 236 |
+
For an example, see
|
| 237 |
+
[ecc-diff-fuzzer/Dockerfile](https://github.com/google/oss-fuzz/blob/master/projects/ecc-diff-fuzzer/Dockerfile).
|
| 238 |
+
where we use `base-builder-rust`and install golang
|
| 239 |
+
|
| 240 |
+
## build.sh {#buildsh}
|
| 241 |
+
|
| 242 |
+
This file defines how to build binaries for [fuzz targets]({{ site.baseurl }}/reference/glossary/#fuzz-target) in your project.
|
| 243 |
+
The script is executed within the image built from your [Dockerfile](#Dockerfile).
|
| 244 |
+
|
| 245 |
+
In general, this script should do the following:
|
| 246 |
+
|
| 247 |
+
- Build the project using your build system with the correct compiler.
|
| 248 |
+
- Provide compiler flags as [environment variables](#Requirements).
|
| 249 |
+
- Build your [fuzz targets]({{ site.baseurl }}/reference/glossary/#fuzz-target) and link your project's build with libFuzzer.
|
| 250 |
+
|
| 251 |
+
Resulting binaries should be placed in `$OUT`.
|
| 252 |
+
|
| 253 |
+
Here's an example from Expat ([source](https://github.com/google/oss-fuzz/blob/master/projects/expat/build.sh)):
|
| 254 |
+
|
| 255 |
+
```bash
|
| 256 |
+
#!/bin/bash -eu
|
| 257 |
+
|
| 258 |
+
./buildconf.sh
|
| 259 |
+
# configure scripts usually use correct environment variables.
|
| 260 |
+
./configure
|
| 261 |
+
|
| 262 |
+
make clean
|
| 263 |
+
make -j$(nproc) all
|
| 264 |
+
|
| 265 |
+
$CXX $CXXFLAGS -std=c++11 -Ilib/ \
|
| 266 |
+
$SRC/parse_fuzzer.cc -o $OUT/parse_fuzzer \
|
| 267 |
+
$LIB_FUZZING_ENGINE .libs/libexpat.a
|
| 268 |
+
|
| 269 |
+
cp $SRC/*.dict $SRC/*.options $OUT/
|
| 270 |
+
```
|
| 271 |
+
|
| 272 |
+
If your project is written in Go, check out the [Integrating a Go project]({{ site.baseurl }}//getting-started/new-project-guide/go-lang/) page.
|
| 273 |
+
|
| 274 |
+
**Note:**
|
| 275 |
+
|
| 276 |
+
1. Don't assume the fuzzing engine is libFuzzer by default, because we generate builds for libFuzzer, AFL++, Honggfuzz, and Centipede fuzzing engine configurations. Instead, link the fuzzing engine using $LIB_FUZZING_ENGINE.
|
| 277 |
+
2. Make sure that the binary names for your [fuzz targets]({{ site.baseurl }}/reference/glossary/#fuzz-target) contain only
|
| 278 |
+
alphanumeric characters, underscore(_) or dash(-). Otherwise, they won't run on our infrastructure.
|
| 279 |
+
3. Don't remove source code files. They are needed for code coverage.
|
| 280 |
+
|
| 281 |
+
### Temporarily disabling code instrumentation during builds
|
| 282 |
+
|
| 283 |
+
In some cases, it's not necessary to instrument every 3rd party library or tool that supports the build target. Use the following snippet to build tools or libraries without instrumentation:
|
| 284 |
+
|
| 285 |
+
|
| 286 |
+
```
|
| 287 |
+
CFLAGS_SAVE="$CFLAGS"
|
| 288 |
+
CXXFLAGS_SAVE="$CXXFLAGS"
|
| 289 |
+
unset CFLAGS
|
| 290 |
+
unset CXXFLAGS
|
| 291 |
+
export AFL_NOOPT=1
|
| 292 |
+
|
| 293 |
+
#
|
| 294 |
+
# build commands here that should not result in instrumented code.
|
| 295 |
+
#
|
| 296 |
+
|
| 297 |
+
export CFLAGS="${CFLAGS_SAVE}"
|
| 298 |
+
export CXXFLAGS="${CXXFLAGS_SAVE}"
|
| 299 |
+
unset AFL_NOOPT
|
| 300 |
+
```
|
| 301 |
+
|
| 302 |
+
### build.sh script environment
|
| 303 |
+
|
| 304 |
+
When your build.sh script is executed, the following locations are available within the image:
|
| 305 |
+
|
| 306 |
+
| Location| Env Variable | Description |
|
| 307 |
+
|---------| ------------ | ---------- |
|
| 308 |
+
| `/out/` | `$OUT` | Directory to store build artifacts (fuzz targets, dictionaries, options files, seed corpus archives). |
|
| 309 |
+
| `/src/` | `$SRC` | Directory to checkout source files. |
|
| 310 |
+
| `/work/`| `$WORK` | Directory to store intermediate files. |
|
| 311 |
+
|
| 312 |
+
Although the files layout is fixed within a container, environment variables are
|
| 313 |
+
provided so you can write retargetable scripts.
|
| 314 |
+
|
| 315 |
+
In case your fuzz target uses the [FuzzedDataProvider] class, make sure it is
|
| 316 |
+
included via `#include <fuzzer/FuzzedDataProvider.h>` directive.
|
| 317 |
+
|
| 318 |
+
[FuzzedDataProvider]: https://github.com/google/fuzzing/blob/master/docs/split-inputs.md#fuzzed-data-provider
|
| 319 |
+
|
| 320 |
+
### build.sh requirements {#Requirements}
|
| 321 |
+
|
| 322 |
+
Only binaries without an extension are accepted as targets. Extensions are reserved for other artifacts, like .dict.
|
| 323 |
+
|
| 324 |
+
You *must* use the special compiler flags needed to build your project and fuzz targets.
|
| 325 |
+
These flags are provided in the following environment variables:
|
| 326 |
+
|
| 327 |
+
| Env Variable | Description
|
| 328 |
+
| ------------- | --------
|
| 329 |
+
| `$CC`, `$CXX`, `$CCC` | The C and C++ compiler binaries.
|
| 330 |
+
| `$CFLAGS`, `$CXXFLAGS` | C and C++ compiler flags.
|
| 331 |
+
| `$LIB_FUZZING_ENGINE` | C++ compiler argument to link fuzz target against the prebuilt engine library (e.g. libFuzzer).
|
| 332 |
+
|
| 333 |
+
You *must* use `$CXX` as a linker, even if your project is written in pure C.
|
| 334 |
+
|
| 335 |
+
Most well-crafted build scripts will automatically use these variables. If not,
|
| 336 |
+
pass them manually to the build tool.
|
| 337 |
+
|
| 338 |
+
See the [Provided Environment Variables](https://github.com/google/oss-fuzz/blob/master/infra/base-images/base-builder/README.md#provided-environment-variables) section in
|
| 339 |
+
`base-builder` image documentation for more details.
|
| 340 |
+
|
| 341 |
+
### Static and dynamic linking of libraries
|
| 342 |
+
The `build.sh` should produce fuzzers that are statically linked. This is because the
|
| 343 |
+
fuzzer build environment is different to the fuzzer runtime environment and if your
|
| 344 |
+
project depends on third party libraries then it is likely they will not be present
|
| 345 |
+
in the execution environment. Thus, any shared libraries you may install or compile in
|
| 346 |
+
`build.sh` or `Dockerfile` will not be present in the fuzzer runtime environment. There
|
| 347 |
+
are exceptions to this rule, and for further information on this please see the [fuzzer environment]({{ site.baseurl }}/further-reading/fuzzer-environment/) page.
|
| 348 |
+
|
| 349 |
+
## Disk space restrictions
|
| 350 |
+
|
| 351 |
+
Our builders have a disk size of 250GB (this includes space taken up by the OS). Builds must keep peak disk usage below this.
|
| 352 |
+
|
| 353 |
+
In addition, please keep the size of the build (everything copied to `$OUT`) small (<10GB uncompressed). The build is repeatedly transferred and unzipped during fuzzing and runs on VMs with limited disk space.
|
| 354 |
+
|
| 355 |
+
## Fuzzer execution environment
|
| 356 |
+
|
| 357 |
+
For more on the environment that
|
| 358 |
+
your [fuzz targets]({{ site.baseurl }}/reference/glossary/#fuzz-target) run in, and the assumptions you can make, see the [fuzzer environment]({{ site.baseurl }}/further-reading/fuzzer-environment/) page.
|
| 359 |
+
|
| 360 |
+
## Testing locally
|
| 361 |
+
|
| 362 |
+
You can build your docker image and fuzz targets locally, so you can test them before you push them to the OSS-Fuzz repository.
|
| 363 |
+
|
| 364 |
+
1. Run the same helper script you used to create your directory structure, this time using it to build your docker image and [fuzz targets]({{ site.baseurl }}/reference/glossary/#fuzz-target):
|
| 365 |
+
|
| 366 |
+
```bash
|
| 367 |
+
$ cd /path/to/oss-fuzz
|
| 368 |
+
$ python infra/helper.py build_image $PROJECT_NAME
|
| 369 |
+
$ python infra/helper.py build_fuzzers --sanitizer <address/memory/undefined> $PROJECT_NAME
|
| 370 |
+
```
|
| 371 |
+
|
| 372 |
+
The built binaries appear in the `/path/to/oss-fuzz/build/out/$PROJECT_NAME`
|
| 373 |
+
directory on your machine (and `$OUT` in the container).
|
| 374 |
+
|
| 375 |
+
**Note:** You *must* run your fuzz target binaries inside the base-runner docker
|
| 376 |
+
container to make sure that they work properly.
|
| 377 |
+
|
| 378 |
+
2. Find failures to fix by running the `check_build` command:
|
| 379 |
+
|
| 380 |
+
```bash
|
| 381 |
+
$ python infra/helper.py check_build $PROJECT_NAME
|
| 382 |
+
```
|
| 383 |
+
|
| 384 |
+
3. If you want to test changes against a particular fuzz target, run the following command:
|
| 385 |
+
|
| 386 |
+
```bash
|
| 387 |
+
$ python infra/helper.py run_fuzzer --corpus-dir=<path-to-temp-corpus-dir> $PROJECT_NAME <fuzz_target>
|
| 388 |
+
```
|
| 389 |
+
|
| 390 |
+
4. We recommend taking a look at your code coverage as a test to ensure that
|
| 391 |
+
your fuzz targets get to the code you expect. This would use the corpus
|
| 392 |
+
generated from the previous `run_fuzzer` step in your local corpus directory.
|
| 393 |
+
|
| 394 |
+
```bash
|
| 395 |
+
$ python infra/helper.py build_fuzzers --sanitizer coverage $PROJECT_NAME
|
| 396 |
+
$ python infra/helper.py coverage $PROJECT_NAME --fuzz-target=<fuzz_target> --corpus-dir=<path-to-temp-corpus-dir>
|
| 397 |
+
```
|
| 398 |
+
|
| 399 |
+
You may need to run `python infra/helper.py pull_images` to use the latest
|
| 400 |
+
coverage tools. Please refer to
|
| 401 |
+
[code coverage]({{ site.baseurl }}/advanced-topics/code-coverage/) for detailed
|
| 402 |
+
information on code coverage generation.
|
| 403 |
+
|
| 404 |
+
|
| 405 |
+
**Note:** Currently, we only support AddressSanitizer (address) and UndefinedBehaviorSanitizer (undefined)
|
| 406 |
+
configurations by default.
|
| 407 |
+
MemorySanitizer is recommended, but needs to be enabled manually since you must build all runtime dependencies with MemorySanitizer.
|
| 408 |
+
<b>Make sure to test each
|
| 409 |
+
of the supported build configurations with the above commands (build_fuzzers -> run_fuzzer -> coverage).</b>
|
| 410 |
+
|
| 411 |
+
If everything works locally, it should also work on our automated builders and ClusterFuzz. If you check in
|
| 412 |
+
your files and experience failures, review your [dependencies]({{ site.baseurl }}/further-reading/fuzzer-environment/#dependencies).
|
| 413 |
+
|
| 414 |
+
## Debugging Problems
|
| 415 |
+
|
| 416 |
+
If you run into problems, our [Debugging page]({{ site.baseurl }}/advanced-topics/debugging/) lists ways to debug your build scripts and
|
| 417 |
+
[fuzz targets]({{ site.baseurl }}/reference/glossary/#fuzz-target).
|
| 418 |
+
|
| 419 |
+
## Efficient fuzzing
|
| 420 |
+
|
| 421 |
+
To improve your fuzz target ability to find bugs faster, you should consider the
|
| 422 |
+
following ways:
|
| 423 |
+
|
| 424 |
+
### Seed Corpus
|
| 425 |
+
|
| 426 |
+
Most fuzzing engines use evolutionary fuzzing algorithms. Supplying a seed
|
| 427 |
+
corpus consisting of good sample inputs is one of the best ways to improve [fuzz
|
| 428 |
+
target]({{ site.baseurl }}/reference/glossary/#fuzz-target)'s coverage.
|
| 429 |
+
|
| 430 |
+
To provide a corpus for `my_fuzzer`, put `my_fuzzer_seed_corpus.zip` file next
|
| 431 |
+
to the [fuzz target]({{ site.baseurl }}/reference/glossary/#fuzz-target)'s binary in `$OUT` during the build. Individual files in this
|
| 432 |
+
archive will be used as starting inputs for mutations. You can store the corpus
|
| 433 |
+
next to source files, generate during build or fetch it using curl or any other
|
| 434 |
+
tool of your choice.
|
| 435 |
+
(example: [boringssl](https://github.com/google/oss-fuzz/blob/master/projects/boringssl/build.sh#L41)).
|
| 436 |
+
|
| 437 |
+
Seed corpus files will be used for cross-mutations and portions of them might appear
|
| 438 |
+
in bug reports or be used for further security research. It is important that corpus
|
| 439 |
+
has an appropriate and consistent license.
|
| 440 |
+
|
| 441 |
+
OSS-Fuzz only: See also [Accessing Corpora]({{ site.baseurl }}/advanced-topics/corpora/) for information about getting access to the corpus we are currently using for your fuzz targets.
|
| 442 |
+
|
| 443 |
+
### Dictionaries
|
| 444 |
+
|
| 445 |
+
Dictionaries hugely improve fuzzing efficiency for inputs with lots of similar
|
| 446 |
+
sequences of bytes. [libFuzzer documentation](https://llvm.org/docs/LibFuzzer.html#dictionaries)
|
| 447 |
+
|
| 448 |
+
Put your dict file in `$OUT`. If the dict filename is the same as your target
|
| 449 |
+
binary name (i.e. `%fuzz_target%.dict`), it will be automatically used. If the
|
| 450 |
+
name is different (e.g. because it is shared by several targets), specify this
|
| 451 |
+
in .options file:
|
| 452 |
+
|
| 453 |
+
```
|
| 454 |
+
[libfuzzer]
|
| 455 |
+
dict = dictionary_name.dict
|
| 456 |
+
```
|
| 457 |
+
|
| 458 |
+
It is common for several [fuzz targets]({{ site.baseurl }}/reference/glossary/#fuzz-target)
|
| 459 |
+
to reuse the same dictionary if they are fuzzing very similar inputs.
|
| 460 |
+
(example: [expat](https://github.com/google/oss-fuzz/blob/ad88a2e5295d91251d15f8a612758cd9e5ad92db/projects/expat/parse_fuzzer.options)).
|
| 461 |
+
|
| 462 |
+
### Input Size
|
| 463 |
+
|
| 464 |
+
By default, the fuzzing engine will generate input of any arbitrary length.
|
| 465 |
+
This might be useful to try corner cases that could lead to a
|
| 466 |
+
security vulnerability. However, if large inputs are not necessary to
|
| 467 |
+
increase the coverage of your target API, it is important to add a limit
|
| 468 |
+
here to significantly improve performance.
|
| 469 |
+
|
| 470 |
+
```cpp
|
| 471 |
+
if (size < kMinInputLength || size > kMaxInputLength)
|
| 472 |
+
return 0;
|
| 473 |
+
```
|
| 474 |
+
|
| 475 |
+
## Checking in to the OSS-Fuzz repository
|
| 476 |
+
|
| 477 |
+
Once you've tested your fuzzing files locally, fork OSS-Fuzz, commit, and push to the fork. Then
|
| 478 |
+
create a pull request with your change. Follow the
|
| 479 |
+
[Forking Project](https://guides.github.com/activities/forking/) guide if you're new to contributing
|
| 480 |
+
via GitHub.
|
| 481 |
+
|
| 482 |
+
### Copyright headers
|
| 483 |
+
|
| 484 |
+
Please include copyright headers for all files checked in to oss-fuzz:
|
| 485 |
+
|
| 486 |
+
```
|
| 487 |
+
# Copyright 2021 Google LLC
|
| 488 |
+
#
|
| 489 |
+
# Licensed under the Apache License, Version 2.0 (the "License");
|
| 490 |
+
# you may not use this file except in compliance with the License.
|
| 491 |
+
# You may obtain a copy of the License at
|
| 492 |
+
#
|
| 493 |
+
# http://www.apache.org/licenses/LICENSE-2.0
|
| 494 |
+
#
|
| 495 |
+
# Unless required by applicable law or agreed to in writing, software
|
| 496 |
+
# distributed under the License is distributed on an "AS IS" BASIS,
|
| 497 |
+
# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
| 498 |
+
# See the License for the specific language governing permissions and
|
| 499 |
+
# limitations under the License.
|
| 500 |
+
#
|
| 501 |
+
################################################################################
|
| 502 |
+
```
|
| 503 |
+
|
| 504 |
+
**Exception:** If you're porting a fuzz target from Chromium, keep the original Chromium license header.
|
| 505 |
+
|
| 506 |
+
## Reviewing results
|
| 507 |
+
|
| 508 |
+
Once your change is merged, your project and fuzz targets should be automatically built and run on
|
| 509 |
+
ClusterFuzz after a short while (< 1 day). If you think there's a problem, you can check your project's [build status](https://oss-fuzz-build-logs.storage.googleapis.com/index.html).
|
| 510 |
+
|
| 511 |
+
Use the [ClusterFuzz web interface](https://oss-fuzz.com/) to review the following:
|
| 512 |
+
* Crashes generated
|
| 513 |
+
* Code coverage statistics
|
| 514 |
+
* Fuzzer statistics
|
| 515 |
+
* Fuzzer performance analyzer (linked from fuzzer statistics)
|
| 516 |
+
|
| 517 |
+
**Note:** Your Google Account must be listed in [project.yaml](#projectyaml) for you to have access to the ClusterFuzz web interface.
|
| 518 |
+
|
| 519 |
+
### Status Badge
|
| 520 |
+
|
| 521 |
+

|
| 523 |
+
|
| 524 |
+
Once your project has started [building](https://oss-fuzz-build-logs.storage.googleapis.com/index.html), we'd love it if you added our badge in
|
| 525 |
+
your project's README. This allows you to see bugs found by your OSS-Fuzz
|
| 526 |
+
integration at a glance. See
|
| 527 |
+
[brotli](https://github.com/google/brotli#introduction)'s
|
| 528 |
+
README for an example.
|
| 529 |
+
|
| 530 |
+
Adding it is super easy, just follow this template:
|
| 531 |
+
```markdown
|
| 532 |
+
[](https://bugs.chromium.org/p/oss-fuzz/issues/list?sort=-opened&can=1&q=proj:<project>)
|
| 533 |
+
```
|
| 534 |
+
|
| 535 |
+
## Monitoring performance via Fuzz Introspector
|
| 536 |
+
|
| 537 |
+
As soon as your project is run with ClusterFuzz (< 1 day), you can view the Fuzz
|
| 538 |
+
Introspector report for your project.
|
| 539 |
+
[Fuzz Introspector](https://github.com/ossf/fuzz-introspector) helps you
|
| 540 |
+
understand your fuzzers' performance and identify any potential blockers.
|
| 541 |
+
It provides individual and aggregated fuzzer reachability and coverage reports.
|
| 542 |
+
You can monitor each fuzzer's static reachability potential and compare it
|
| 543 |
+
against dynamic coverage and identify any potential bottlenecks.
|
| 544 |
+
Fuzz Introspector can offer suggestions on increasing coverage by adding new
|
| 545 |
+
fuzz targets or modify existing ones.
|
| 546 |
+
Fuzz Introspector reports can be viewed from the [OSS-Fuzz
|
| 547 |
+
homepage](https://oss-fuzz.com/) or through this
|
| 548 |
+
[index](http://oss-fuzz-introspector.storage.googleapis.com/index.html).
|
| 549 |
+
Fuzz Introspector support C and C++ projects.
|
| 550 |
+
Support for Java and Python projects is in the progress.
|
| 551 |
+
|
| 552 |
+
You can view the [Fuzz Introspector report for bzip2](https://storage.googleapis.com/oss-fuzz-introspector/bzip2/inspector-report/20221017/fuzz_report.html)
|
| 553 |
+
as an example.
|
local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/oss-fuzz/architecture.md
ADDED
|
@@ -0,0 +1,33 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Architecture
|
| 4 |
+
permalink: /architecture/
|
| 5 |
+
nav_order: 1
|
| 6 |
+
parent: OSS-Fuzz
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Architecture
|
| 10 |
+

|
| 11 |
+
|
| 12 |
+
The process works like this:
|
| 13 |
+
|
| 14 |
+
1. A maintainer of an open source project (or an outside volunteer) creates
|
| 15 |
+
one or more [fuzz targets](https://llvm.org/docs/LibFuzzer.html#fuzz-target)
|
| 16 |
+
and [integrates]({{ site.baseurl }}/advanced-topics/ideal-integration/) them
|
| 17 |
+
with the project's build and test system.
|
| 18 |
+
1. The project is [accepted to OSS-Fuzz]({{ site.baseurl }}/getting-started/accepting-new-projects/) and the developer commits their build configurations.
|
| 19 |
+
1. The OSS-Fuzz [builder](https://github.com/google/oss-fuzz/tree/master/infra/build) builds the project from the committed configs.
|
| 20 |
+
1. The builder uploads the fuzz targets to the OSS-Fuzz GCS bucket.
|
| 21 |
+
1. [ClusterFuzz]({{ site.baseurl }}/further-reading/clusterfuzz) downloads the fuzz targets and begins to fuzz the projects.
|
| 22 |
+
1. When Clusterfuzz finds a
|
| 23 |
+
bug, it reports the issue automatically to the OSS-Fuzz
|
| 24 |
+
[issue tracker](https://bugs.chromium.org/p/oss-fuzz/issues/list)
|
| 25 |
+
([example](https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=9)).
|
| 26 |
+
([Why use a different tracker?]({{ site.baseurl }}/faq/#why-do-you-use-a-different-issue-tracker-for-reporting-bugs-in-oss-projects))
|
| 27 |
+
1. Project owners are CCed on the bug report.
|
| 28 |
+
1. The project developer fixes the bug upstream and credits OSS-Fuzz for the
|
| 29 |
+
discovery (the commit message should contain the string **'Credit to OSS-Fuzz'**).
|
| 30 |
+
|
| 31 |
+
Once the developer fixes the bug, [ClusterFuzz]({{ site.baseurl }}/further-reading/clusterfuzz) automatically
|
| 32 |
+
verifies the fix, adds a comment, and closes the issue ([example](https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=53#c3)). After the fix is verified or 90 days after reporting (whichever is earlier), the issue becomes [public]({{ site.baseurl }}/getting-started/bug-disclosure-guidelines/).
|
| 33 |
+
|
local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/reference/glossary.md
ADDED
|
@@ -0,0 +1,99 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Glossary
|
| 4 |
+
nav_order: 1
|
| 5 |
+
permalink: /reference/glossary/
|
| 6 |
+
parent: Reference
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Glossary
|
| 10 |
+
|
| 11 |
+
For general fuzzing terms, see the [glossary] from [google/fuzzing] project.
|
| 12 |
+
|
| 13 |
+
[glossary]: https://github.com/google/fuzzing/blob/master/docs/glossary.md
|
| 14 |
+
[google/fuzzing]: https://github.com/google/fuzzing
|
| 15 |
+
|
| 16 |
+
- TOC
|
| 17 |
+
{:toc}
|
| 18 |
+
---
|
| 19 |
+
|
| 20 |
+
## OSS-Fuzz specific terms
|
| 21 |
+
|
| 22 |
+
### ClusterFuzz
|
| 23 |
+
|
| 24 |
+
A scalable fuzzing infrastructure that is used for OSS-Fuzz backend.
|
| 25 |
+
[ClusterFuzz] is also used to fuzz Chrome and many other projects. A quick
|
| 26 |
+
overview of ClusterFuzz user interface is available on this [page].
|
| 27 |
+
|
| 28 |
+
[page]: {{ site.baseurl }}/further-reading/clusterfuzz
|
| 29 |
+
[ClusterFuzz]: https://github.com/google/clusterfuzz
|
| 30 |
+
|
| 31 |
+
### Fuzz Target
|
| 32 |
+
|
| 33 |
+
In addition to its
|
| 34 |
+
[general definition](https://github.com/google/fuzzing/blob/master/docs/glossary.md#fuzz-target),
|
| 35 |
+
in OSS-Fuzz a fuzz target can be used to
|
| 36 |
+
[reproduce bug reports]({{ site.baseurl }}/advanced-topics/reproducing/).
|
| 37 |
+
It is recommended to use it for regression testing as well (see
|
| 38 |
+
[ideal integration]({{ site.baseurl }}/advanced-topics/ideal-integration/)).
|
| 39 |
+
|
| 40 |
+
### Job type
|
| 41 |
+
|
| 42 |
+
Or **Fuzzer Build**.
|
| 43 |
+
|
| 44 |
+
This refers to a build that contains all the [fuzz targets] for a given
|
| 45 |
+
[project](#project), is run with a specific [fuzzing engine], in a specific
|
| 46 |
+
build mode (e.g. with enabled/disabled assertions), and optionally combined
|
| 47 |
+
with a [sanitizer].
|
| 48 |
+
|
| 49 |
+
For example, we have a "libfuzzer_asan_sqlite" job type, indicating a build of
|
| 50 |
+
all sqlite3 [fuzz targets] using [libFuzzer](http://libfuzzer.info) and
|
| 51 |
+
[ASan](http://clang.llvm.org/docs/AddressSanitizer.html).
|
| 52 |
+
|
| 53 |
+
### Project
|
| 54 |
+
|
| 55 |
+
A project is an open source software project that is integrated with OSS-Fuzz.
|
| 56 |
+
Each project has a single set of configuration files
|
| 57 |
+
(example: [expat](https://github.com/google/oss-fuzz/tree/master/projects/expat))
|
| 58 |
+
and may have one or more [fuzz targets]
|
| 59 |
+
(example: [openssl](https://github.com/openssl/openssl/blob/master/fuzz/)).
|
| 60 |
+
|
| 61 |
+
### Reproducer
|
| 62 |
+
|
| 63 |
+
Or a **testcase**.
|
| 64 |
+
|
| 65 |
+
A [test input] that causes a specific bug to reproduce.
|
| 66 |
+
|
| 67 |
+
[fuzz targets]: https://github.com/google/fuzzing/blob/master/docs/glossary.md#fuzz-target
|
| 68 |
+
[fuzzing engine]: https://github.com/google/fuzzing/blob/master/docs/glossary.md#fuzzing-engine
|
| 69 |
+
[sanitizer]: https://github.com/google/fuzzing/blob/master/docs/glossary.md#sanitizer
|
| 70 |
+
[test input]: https://github.com/google/fuzzing/blob/master/docs/glossary.md#test-input
|
| 71 |
+
|
| 72 |
+
### Sanitizers
|
| 73 |
+
|
| 74 |
+
Fuzzers are usually built with one or more [sanitizer](https://github.com/google/sanitizers) enabled.
|
| 75 |
+
|
| 76 |
+
```bash
|
| 77 |
+
$ python infra/helper.py build_fuzzers --sanitizer undefined json
|
| 78 |
+
```
|
| 79 |
+
|
| 80 |
+
Supported sanitizers:
|
| 81 |
+
|
| 82 |
+
| Sanitizer | Description
|
| 83 |
+
| ------------ | ----------
|
| 84 |
+
| `address` *(default)* | [Address Sanitizer](https://github.com/google/sanitizers/wiki/AddressSanitizer) with [Leak Sanitizer](https://github.com/google/sanitizers/wiki/AddressSanitizerLeakSanitizer).
|
| 85 |
+
| `undefined` | [Undefined Behavior Sanitizer](http://clang.llvm.org/docs/UndefinedBehaviorSanitizer.html).
|
| 86 |
+
| `memory` | [Memory Sanitizer](https://github.com/google/sanitizers/wiki/MemorySanitizer).<br/>*NOTE: It is critical that you build __all__ the code in your program (including libraries it uses) with Memory Sanitizer. Otherwise, you will see false positive crashes due to an inability to see initializations in uninstrumented code.*
|
| 87 |
+
| `coverage` | Used for generating code coverage reports. See [Code Coverage doc]({{ site.baseurl }}/advanced-topics/code-coverage/).
|
| 88 |
+
|
| 89 |
+
Compiler flag values for predefined configurations are specified in the [Dockerfile](https://github.com/google/oss-fuzz/blob/master/infra/base-images/base-builder/Dockerfile).
|
| 90 |
+
These flags can be overridden by specifying `$SANITIZER_FLAGS` directly.
|
| 91 |
+
|
| 92 |
+
You can choose which configurations to automatically run your fuzzers with in `project.yaml` file (e.g. [sqlite3](https://github.com/google/oss-fuzz/tree/master/projects/sqlite3/project.yaml)).
|
| 93 |
+
|
| 94 |
+
### Architectures
|
| 95 |
+
ClusterFuzz supports fuzzing on x86_64 (aka x64) by default. However you can also fuzz using AddressSanitizer and libFuzzer on i386 (aka x86, or 32 bit) by specifying the `$ARCHITECTURE` build environment variable using the `--architecture` option:
|
| 96 |
+
|
| 97 |
+
```bash
|
| 98 |
+
python infra/helper.py build_fuzzers --architecture i386 json
|
| 99 |
+
```
|
local-test-commons-compress-full-01-vuln_0/fuzz-tooling/docs/reference/reference.md
ADDED
|
@@ -0,0 +1,9 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
---
|
| 2 |
+
layout: default
|
| 3 |
+
title: Reference
|
| 4 |
+
has_children: true
|
| 5 |
+
nav_order: 6
|
| 6 |
+
permalink: /reference/
|
| 7 |
+
---
|
| 8 |
+
|
| 9 |
+
# Reference
|