text stringlengths 454 608k | url stringlengths 17 896 | dump stringclasses 91
values | source stringclasses 1
value | word_count int64 101 114k | flesch_reading_ease float64 50 104 |
|---|---|---|---|---|---|
May 20, 2021
Bioconductors:
We are pleased to announce Bioconductor 3.13, consisting of 2042 software packages, 406 experiment data packages, 965 annotation packages, and 29 workflows.
There are 133 new software packages, 22 new data experiment packages, 7 new annotation packages, 1 new workflow, no new books, and many updates and improvements to existing packages; Bioconductor 3.13 is compatible with R 4.1.0, and is supported on Linux, 32- and 64-bit Windows, and macOS 10.14.6 Mojave or higher. This release will include an updated Bioconductor Docker containers.
Thank you to everyone for your contribution to Bioconductor
Visit Bioconductor BiocViews for details and downloads.
To update to or install Bioconductor 3.13:
Install R 4.1.0. Bioconductor 3.13 has been designed expressly for this version of R.
Follow the instructions at Installing Bioconductor.
There are 133 new software packages in this release of Bioconductor.
airpart.
autonomics This package offers a generic and intuitive solution for cross-platform omics data analysis. It has functions for import, preprocessing, exploration, contrast analysis and visualization of omics data. It follows a tidy, functional programming paradigm.
awst.
barcodetrackR barcodetrackR is an R package developed for the analysis and visualization of clonal tracking data. Data required is samples and tag abundances in matrix form. Usually from cellular barcoding experiments, integration site retrieval analyses, or similar technologies.
biodb.
BioNERO.
BloodGen3Module.
bnem).
BumpyMatrix.
CAEN.
cbpManager This R package provides an R Shiny application that enables the user to generate, manage, and edit data and metadata files suitable for the import in cBioPortal for Cancer Genomics. Create cancer studies and edit its metadata. Upload mutation data of a patient that will be concatenated to the data_mutation_extended.txt file of the study. Create and edit clinical patient data, sample data, and timeline data. Create custom timeline tracks for patients.
CelliD.
cellmigRation Import TIFF images of fluorescently labeled cells, and track cell movements over time. Parallelization is supported for image processing and for fast computation of cell trajectories. In-depth analysis of cell trajectories is enabled by 15 trajectory analysis functions.
censcyt Methods for differential abundance analysis in high-dimensional cytometry data when a covariate is subject to right censoring (e.g. survival time) based on multiple imputation and generalized linear mixed models.
CIMICE.
CNVgears.
CNViz CNViz takes probe, gene, and segment-level log2 copy number ratios and launches a Shiny app to visualize your sample’s copy number profile. You can also integrate loss of heterozygosity (LOH) and single nucleotide variant (SNV) data.
ComPrAn This package is for analysis of SILAC labeled complexome profiling data. It uses peptide table in tab-delimited format as an input and produces ready-to-use tables and plots.
conclus.
condiments This package encapsulate many functions to conduct a differential topology analysis. It focuses on analyzing an ‘omic dataset with multiple conditions. While the package is mostly geared toward scRNASeq, it does not place any restriction on the actual input format.
CON.
cosmosR COSMOS (Causal Oriented Search of Multi-Omic Space) is a method that integrates phosphoproteomics, transcriptomics, and metabolomics data sets based on prior knowledge of signaling, metabolic, and gene regulatory networks. It estimated the activities of transcrption factors and kinases and finds a network-level causal reasoning. Thereby, COSMOS provides mechanistic hypotheses for experimental observations across mulit-omics datasets.
CTDquerier Package to retrieve and visualize data from the Comparative Toxicogenomics Database (). The downloaded data is formated as DataFrames for further downstream analyses.
cyanoFilter.
CytoGLMM.
dce.
decoupleR.
DeepPINCS The identification of novel compound-protein interaction (CPI) is important in drug discovery. Revealing unknown compound-protein interactions is useful to design a new drug for a target protein by screening candidate compounds. The accurate CPI prediction assists in effective drug discovery process. To identify potential CPI effectively, prediction methods based on machine learning and deep learning have been developed. Data for sequences are provided as discrete symbolic data. In the data, compounds are represented as SMILES (simplified molecular-input line-entry system) strings and proteins are sequences in which the characters are amino acids. The outcome is defined as a variable that indicates how strong two molecules interact with each other or whether there is an interaction between them. In this package, a deep-learning based model that takes only sequence information of both compounds and proteins as input and the outcome as output is used to predict CPI. The model is implemented by using compound and protein encoders with useful features. The CPI model also supports other modeling tasks, including protein-protein interaction (PPI), chemical-chemical interaction (CCI), or single compounds and proteins. Although the model is designed for proteins, DNA and RNA can be used if they are represented as sequences.
DelayedRandomArray.
DExMA performing all the steps of gene expression meta-analysis without eliminating those genes that are presented in almost two data sets. It provides the necessary functions to be able to perform the different methods of gene expression meta-analysis. In addition, it contains functions to apply quality controls, download GEO data sets and show graphical representations of the results.
diffUTR.
dir.expiry Implements an expiration system for access to versioned directories. Directories that have not been accessed by a registered function within a certain time frame are deleted. This aims to reduce disk usage by eliminating obsolete caches generated by old versions of packages.
drugTargetInteractions.
epialleleR computing the empirical cumulative distribution function for per-read beta values, and testing the significance of the association between epiallele methylation status and base frequencies at particular genomic positions (SNPs).
epidecodeR.
epigraHMM epigraHMM provides a set of tools for the analysis of epigenomic data based on hidden Markov Models. It contains two separate peak callers, one for consensus peaks from biological/technical replicates, and and one for differial peaks from multi-replicate multi-condition experiments. For the latter, window-specific posterior probabilities associated with read count enrichment for every possible combinatorial pattern are provided..
FEAST.
fedup.
fgga Package that implements the FGGA algorithm. This package provides a hierarchical ensemble method based ob factor graphs for the consistent GO annotation of protein coding genes. FGGA embodies elements of predicate logic, communication theory, supervised learning and inference in graphical models.
flowGraph Identifies maximal differential cell populations in flow cytometry data taking into account dependencies between cell populations; flowGraph calculates and plots SpecEnr abundance scores given cell population cell counts.
fobitools A set of tools for interacting with Food-Biomarker Ontology (FOBI). A collection of basic manipulation tools for biological significance analysis, graphs, and text mining strategies for annotating nutritional data.
GenomicDistributions If you have a set of genomic ranges, this package can help you with visualization and comparison. It produces several kinds of plots, for example: Chromosome distribution plots, which visualize how your regions are distributed over chromosomes; feature distance distribution plots, which visualizes how your regions are distributed relative to a feature of interest, like Transcription Start Sites (TSSs); genomic partition plots, which visualize how your regions overlap given genomic features such as promoters, introns, exons, or intergenic regions. It also makes it easy to compare one set of ranges to another.
GenomicSuperSignature This package contains the index, which is the Replicable and interpretable Axes of Variation (RAV) extracted from public RNA sequencing datasets by clustering and averaging top PCs. This index, named as RAVindex, is further annotated with MeSH terms and GSEA. Functions to connect PCs from new datasets to RAVs, extract interpretable annotations, and provide intuitive visualization, are implemented in this package. Overall, this package enables researchers to analyze new data in the context of existing databases with minimal computing resources.
GEOfastq GEOfastq is used to download fastq files from the European Nucleotide Archive (ENA) starting with an accession from the Gene Expression Omnibus (GEO). To do this, sample metadata is retrieved from GEO and the Sequence Read Archive (SRA). SRA run accessions are then used to construct FTP and aspera download links for fastq files generated by the ENA.
GeomxTools Tools for NanoString Technologies GeoMx Technology. Package provides functions for reading in DCC and PKC files based on an ExpressionSet derived object. Normalization and QC functions are also included.
geva.
granulator granulator is an R package for the cell type deconvolution of heterogeneous tissues based on bulk RNA-seq data or single cell RNA-seq expression profiles. The package provides a unified testing interface to rapidly run and benchmark multiple state-of-the-art deconvolution methods. Data for the deconvolution of peripheral blood mononuclear cells (PBMCs) into individual immune cell types is provided as well.
hca This package provides users with the ability
to query the Human Cell Atlas data repository for single-cell
experiment data. The
projects(),
files(),
samples() and
bundles() functions retrieve summary information on each of these
indexes; corresponding
*_details() are available for individual
entries of each index. File-based resources can be downloaded using
files_download(). Advanced use of the package allows the user to
page through large result sets, and to flexibly query the
‘list-of-lists’ structure representing query responses.
HGC
HGC (short for Hierarchical Graph-based
Clustering) is a R package for conducting hierarchical clustering
on large-scale single-cell RNA-seq (scRNA-seq) data. The key idea
is to construct a dendrogram of cells on their shared nearest
neighbor (SNN) graph.
HGC provides functions for building cell
graphs and for conducting hierarchical clustering on the graph.
HiCDCPlus.
HubPub.
immunotation.
interacCircos Implement in an efficient approach to display the genomic data, relationship, information in an interactive circular genome(Circos) plot. ‘interacCircos’ are inspired by ‘circosJS’, ‘BioCircos.js’ and ‘NG-Circos’ and we integrate the modules of ‘circosJS’, ‘BioCircos.js’ and ‘NG-Circos’ into this R package, based on ‘htmlwidgets’ framework.
InteractiveComplexHeatmap This package can easily make heatmaps which are produced by the ComplexHeatmap package into interactive applications. It provides two types of interactivities: 1. on the interactive graphics device, and 2. on a Shiny app. It also provides functions for integrating the interactive heatmap widgets for more complex Shiny app development.
InterCellar, the user can define interaction-pairs modules and link them to significant functional terms from Pathways or Gene Ontology.
IRISFGM.
KBoost.
lisaClust.
LRcell The goal of LRcell is to identify specific sub-cell types that drives the changes observed in a bulk RNA-seq differential gene expression experiment. To achieve this, LRcell utilizes sets of cell marker genes acquired from single-cell RNA-sequencing (scRNA-seq) as indicators for various cell types in the tissue of interest. Next, for each cell type, using its marker genes as indicators, we apply Logistic Regression on the complete set of genes with differential expression p-values to calculate a cell-type significance p-value. Finally, these p-values are compared to predict which one(s) are likely to be responsible for the differential gene expression pattern observed in the bulk RNA-seq experiments. LRcell is inspired by the LRpath[@sartor2009lrpath] algorithm developed by Sartor et al., originally designed for pathway/gene set enrichment analysis. LRcell contains three major components: LRcell analysis, plot generation and marker gene selection. All modules in this package are written in R. This package also provides marker genes in the Prefrontal Cortex (pFC) human brain region, human PBMC and nine mouse brain regions (Frontal Cortex, Cerebellum, Globus Pallidus, Hippocampus, Entopeduncular, Posterior Cortex, Striatum, Substantia Nigra and Thalamus).
MACSr The Model-based Analysis of ChIP-Seq (MACS) is a widely used toolkit for identifying transcript factor binding sites. This package is an R wrapper of the lastest MACS3.
MAGAR .
MatrixQCvis Data quality assessment is an integral part of preparatory data analysis to ensure sound biological information retrieval. We present here the MatrixQCvis package, which provides shiny-based interactive visualization of data quality metrics at the per-sample and per-feature level. It is broadly applicable to quantitative omics data types that come in matrix-like format (features x samples). It enables the detection of low-quality samples, drifts, outliers and batch effects in data sets. Visualizations include amongst others bar- and violin plots of the (count/intensity) values, mean vs standard deviation plots, MA plots, empirical cumulative distribution function (ECDF) plots, visualizations of the distances between samples, and multiple types of dimension reduction plots. Furthermore, MatrixQCvis allows for differential expression analysis based on the limma (moderated t-tests) and proDA (Wald tests) packages. MatrixQCvis builds upon the popular Bioconductor SummarizedExperiment S4 class and enables thus the facile integration into existing workflows. The package is especially tailored towards metabolomics and proteomics mass spectrometry data, but also allows to assess the data quality of other data types that can be represented in a SummarizedExperiment object.
memes A seamless interface to the MEME Suite family of tools for motif analysis. ‘memes’ provides data aware utilities for using GRanges objects as entrypoints to motif analysis, data structures for examining & editing motif lists, and novel data visualizations. ‘memes’ functions and data structures are amenable to both base R and tidyverse workflows.
MetaboCoreUtils MetaboCoreUtils defines metabolomics-related core functionality provided as low-level functions to allow a data structure-independent usage across various R packages. This includes functions to calculate between ion (adduct) and compound mass-to-charge ratios and masses or functions to work with chemical formulas. The package provides also a set of adduct definitions and information on some commercially available internal standard mixes commonly used in MS experiments.
metapod.
methylscaper methylscaper is an R package for processing and visualizing data jointly profiling methylation and chromatin accessibility (MAPit, NOMe-seq, scNMT-seq, nanoNOMe, etc.). The package supports both single-cell and single-molecule data, and a common interface for jointly visualizing both data types through the generation of ordered representational methylation-state matrices. The Shiny app allows for an interactive seriation process of refinement and re-weighting that optimally orders the cells or DNA molecules to discover methylation patterns and nucleosome positioning.
mia.
miaViz miaViz implements plotting function to work with TreeSummarizedExperiment and related objects in a context of microbiome analysis. Among others this includes plotting tree, graph and microbiome series data.
midasHLA MiDAS is a R package for immunogenetics data transformation and statistical analysis. MiDAS accepts input data in the form of HLA alleles and KIR types, and can transform it into biologically meaningful variables, enabling HLA amino acid fine mapping, analyses of HLA evolutionary divergence, KIR gene presence, as well as validated HLA-KIR interactions. Further, it allows comprehensive statistical association analysis workflows with phenotypes of diverse measurement scales. MiDAS closes a gap between the inference of immunogenetic variation and its efficient utilization to make relevant discoveries related to T cell, Natural Killer cell, and disease biology.
miloR This package performs single-cell differential abundance testing. Cell states are modelled as representative neighbourhoods on a nearest neighbour graph. Hypothesis testing is performed using a negative bionomial generalized linear model.
mina.
miQC.
mirTarRnaSeq.
mistyR mistyR is an impolementation.
moanin.
ModCon.
MQmetrics.
MsBackendMassbank Mass spectrometry (MS) data backend supporting import and export of MS/MS library spectra from MassBank record files. Different backends are available that allow handling of data in plain MassBank text file format or allow also to interact directly with MassBank SQL databases. Objects from this package are supposed to be used with the Spectra Bioconductor package. This package thus adds MassBank support to the Spectra package.
MsBackendMgfFeatures.
msqrob2 msqrob2 provides a robust linear mixed model framework for assessing differential abundance in MS-based Quantitative proteomics experiments. Our workflows can start from raw peptide intensities or summarised protein expression values. The model parameter estimates can be stabilized by ridge regression, empirical Bayes variance estimation and robust M-estimation. msqrob2’s hurde workflow can handle missing data without having to rely on hard-to-verify imputation assumptions, and, outcompetes state-of-the-art methods with and without imputation for both high and low missingness. It builds on QFeature infrastructure for quantitative mass spectrometry data to store the model results together with the raw data and preprocessed data.
MSstatsLOBD) <doi:10.1074/mcp.RA117.000322>.
multiSight multiSight is an R package providing an user-friendly graphical interface to analyze your omic datasets in a multi-omics manner based on Stouffer’s p-value pooling and multi-block statistical methods. For each omic dataset you furnish, multiSight provides classification models with feature selection you can use as biosignature: (i) To forecast phenotypes (e.g. to diagnostic tasks, histological subtyping), (ii) To design Pathways and gene ontology enrichments (Over Representation Analysis), (iii) To build Network inference linked to PubMed querying to make assumptions easier and data-driven.
mumosa Assorted utilities for multi-modal analyses of single-cell datasets. Includes functions to combine multiple modalities for downstream analysis, perform MNN-based batch correction across multiple modalities, and to compute correlations between assay values for different modalities.
MungeSumstats.
NanoStringNCTools Tools for NanoString Technologies nCounter Technology. Provides support for reading RCC files into an ExpressionSet derived object. Also includes methods for QC and normalizaztion of NanoString data.
nempi.
ORFhunteR.
PDATK.
PFP.
PhenoGeneRanker..
PhIPData.
planet.
PoDCall Reads files exported from ‘QuantaSoft’ containing amplitude values from a run of ddPCR (96 well plate) and robustly sets thresholds to determine positive droplets for each channel of each individual well. Concentration and normalized concentration in addition to other metrics is then calculated for each well. Results are returned as a table, optionally written to file, as well as optional plots (scatterplot and histogram) for both channels per well written to file. The package includes a shiny application which provides an interactive and user-friendly interface to the full functionality of PoDCall.
POW.
ppcseq.
ptairMS This package implements a suite of methods to preprocess data from PTR-TOF-MS instruments (HDF5 format) and generates the ‘sample by features’ table of peak intensities in addition to the sample and feature metadata (as a single ExpressionSet object for subsequent statistical analysis). This package also permit usefull tools for cohorts management as analyzing data progressively, visualization tools and quality control. The steps include calibration, expiration detection, peak detection and quantification, feature alignment, missing value imputation and feature annotation. Applications to exhaled air and cell culture in headspace are described in the vignettes and examples. This package was used for data analysis of Gassin Delyle study on adults undergoing invasive mechanical ventilation in the intensive care unit due to severe COVID-19 or non-COVID-19 acute respiratory distress syndrome (ARDS), and permit to identfy four potentiel biomarquers of the infection.
quantiseqr.
ramr ramr is an R package for detection of low-frequency aberrant methylation events in large datasets obtained by methylation profiling using array or high-throughput bisulfite sequencing. In addition, package provides functions to visualize found aberrantly methylated regions (AMRs), and to generate sets of all possible regions to be used as reference sets for enrichment analysis.
rawrr This package wraps the functionality of the RawFileReader .NET assembly. Within the R environment, spectra and chromatograms are represented by S3 objects (Kockmann T. et al. (2020) <doi:10.1101/2020.10.30.362533>). The package provides basic functions to download and install the required third-party libraries. The package is developed, tested, and used at the Functional Genomics Center Zurich, Switzerland.
Rbec.
RCSL A novel clustering algorithm and toolkit RCSL (Rank Constrained Similarity Learning) to accurately identify various cell types using scRNA-seq data from a complex tissue. RCSL considers both lo-cal similarity and global similarity among the cells to discern the subtle differences among cells of the same type as well as larger differences among cells of different types. RCSL uses Spearman’s rank correlations of a cell’s expression vector with those of other cells to measure its global similar-ity, and adaptively learns neighbour representation of a cell as its local similarity. The overall similar-ity of a cell to other cells is a linear combination of its global similarity and local similarity.
ReactomeContentService4R.
ReactomeGraph4R.
RiboDiPA This package performs differential pattern analysis for Ribo-seq data. It identifies genes with significantly different patterns in the ribosome footprint between two conditions. RiboDiPA contains five major components including bam file processing, P-site mapping, data binning, differential pattern analysis and footprint visualization.
RLassoCox.
SANTA).
satuRn.
ScaledMatrix Provides delayed computation of a matrix of scaled and centered values. The result is equivalent to using the scale() function but avoids explicit realization of a dense matrix during block processing. This permits greater efficiency in common operations, most notably matrix multiplication.
SCArray.
scClassifR The package comprises a set of pretrained machine learning models to predict basic immune cell types. This enables all users to quickly get a first annotation of the cell types present in their dataset without requiring prior knowledge. scClassifR also allows users to train their own models to predict new cell types based on specific research needs.
sechm.
shinyepico.
SingleMoleculeFootprinting
sitadela.
SOMNiBUS This package aims to analyse count-based methylation data on predefined genomic regions, such as those obtained by targeted sequencing, and thus to identify differentially methylated regions (DMRs) that are associated with phenotypes or traits. The method is built a rich flexible model that allows for the effects, on the methylation levels, of multiple covariates to vary smoothly along genomic regions. At the same time, this method also allows for sequencing errors and can adjust for variability in cell type mixture.
SplicingFactory.
Summix This package contains the Summix method for estimating and adjusting for ancestry in genetic summary allele frequency data. The function summix estimates reference ancestry proportions using a mixture model. The adjAF function produces ancestry adjusted allele frequencies for an observed sample with ancestry proportions matching a target person or sample.
supersigs).
systemPipeTools.
tLOH).
TrajectoryGeometry.
TrajectoryUtils Implements low-level utilities for single-cell trajectory analysis, primarily intended for re-use inside higher-level packages. Include a function to create a cluster-level minimum spanning tree and data structures to hold pseudotime inference results.
TraRe).
Travel.
treekoR.
tricycle The package contains functions to infer and visualize cell cycle process using Single Cell RNASeq data. It exploits the idea of transfer learning, projecting new data to the previous learned biologically interpretable space. We provide a pre-learned cell cycle space, which could be used to infer cell cycle time of human and mouse single cell samples. In addition, we also offer functions to visualize cell cycle time on different embeddings and functions to build new reference.
ttgsea Functional enrichment analysis methods such as gene set enrichment analysis (GSEA) have been widely used for analyzing gene expression data. GSEA is a powerful method to infer results of gene expression data at a level of gene sets by calculating enrichment scores for predefined sets of genes. GSEA depends on the availability and accuracy of gene sets. There are overlaps between terms of gene sets or categories because multiple terms may exist for a single biological process, and it can thus lead to redundancy within enriched terms. In other words, the sets of related terms are overlapping. Using deep learning, this pakage is aimed to predict enrichment scores for unique tokens or words from text in names of gene sets to resolve this overlapping set issue. Furthermore, we can coin a new term by combining tokens and find its enrichment score by predicting such a combined tokens.
VarCon VarCon is an R package which converts the positional information from the annotation of an single nucleotide variation (SNV) (either referring to the coding sequence or the reference genomic sequence). It retrieves the genomic reference sequence around the position of the single nucleotide variation. To asses, whether the SNV could potentially influence binding of splicing regulatory proteins VarCon calcualtes the HEXplorer score as an estimation. Besides, VarCon additionally reports splice site strengths of splice sites within the retrieved genomic sequence and any changes due to the SNV.
vissE.
wppi Protein-protein interaction data is essential for omics data analysis and modeling. Database knowledge is general, not specific for cell type, physiological condition or any other context determining which connections are functional and contribute to the signaling. Functional annotations such as Gene Ontology and Human Phenotype Ontology might help to evaluate the relevance of interactions. This package predicts functional relevance of protein-protein interactions based on functional annotations such as Human Protein Ontology and Gene Ontology, and prioritizes genes based on network topology, functional scores and a path search algorithm.
XNAString.
There are 22 new data experiment packages in this release of Bioconductor.
BeadSorted.Saliva.EPIC Raw data objects used to estimate saliva cell proportion estimates in ewastools. The FlowSorted.Saliva.EPIC object is constructed from saples assayed by Lauren Middleton et. al. (2021).
BioImageDbs The package provides a bioimage dataset for the image analysis using machine learning and deep learning. The dataset includes microscopy imaging data with supervised labels. The data is provided as R list data that can be loaded to Keras/tensorflow in R.
DExMAdata Data objects needed to allSameID() function of DExMA package. There are also some objects that are necessary to be able to apply the examples of the DExMA package, which illustrate package functionality.
emtdata This package provides pre-processed RNA-seq data where the epithelial to mesenchymal transition was induced on cell lines. These data come from three publications Cursons et al. (2015), Cursons etl al. (2018) and Foroutan et al. (2017). In each of these publications, EMT was induces across multiple cell lines following treatment by TGFb among other stimulants. This data will be useful in determining the regulatory programs modified in order to achieve an EMT. Data were processed by the Davis laboratory in the Bioinformatics division at WEHI.
ewceData This package provides reference data required for ewce. Expression Weighted Celltype Enrichment (EWCE).
GenomicDistributionsData This package provides ready to use reference data for GenomicDistributions package. Raw data was obtained from ensembldb and processed with helper functions. Data files are available for the following genome assemblies: hg19, hg38, mm9 and mm10.
GSE13015.
imcdatasets.
LRcellTypeMarkers This is an external ExperimentData package for LRcell. This data package contains the gene enrichment scores calculated from scRNA-seq dataset which indicates the gene enrichment of each cell type in certain brain region. LRcell package is used to identify specific sub-cell types that drives the changes observed in a bulk RNA-seq differential gene expression experiment. For more details, please visit:.
MACSdata Test datasets from the MACS3 test
examples are use in the examples of the
MACSr package. All 9
datasets are uploaded to the
ExperimentHub. The original data can
be found at:.
methylclockData Collection of 9 datasets, andrews and bakulski cord blood, blood gse35069, blood gse35069 chen, blood gse35069 complete, combined cord blood, cord bloo d gse68456, gervin and lyle cord blood, guintivano dlpfc and saliva gse48472”. Data downloaded from meffil. Data used to estimate cell counts using Extrinsic epigenetic age acceleration (EEAA) method Collection of 12 datasets to use with MethylClock package to estimate chronological and gestational DNA methylationwith estimators to use wit different methylation clocks
microbiomeDataSets.
MouseThymusAgeing.
msigdb.
ObMiTi The package provide RNA-seq count for 2 strains of mus musclus; Wild type and Ob/Ob. Each strain was divided into two groups, and each group received either chow diet or high fat diet. RNA expression was measured after 12 weeks in 7 tissues.
preciseTADhub An experimentdata package to supplement the preciseTAD package containing pre-trained models and the variable importances of each genomic annotation used to build the model parsed into list objects and available in ExperimentHub. In total, preciseTADhub provides access to n=84 random forest classification models optimized to predict TAD/chromatin loop boundary regions and stored as .RDS files. The value, n, comes from the fact that we considered l=2 cell lines {GM12878, K562}, g=2 ground truth boundaries {Arrowhead, Peakachu}, and c=21 autosomal chromosomes {CHR1, CHR2, …, CHR22} (omitting CHR9). Furthermore, each object is itself a two-item list containing: (1) the model object, and (2) the variable importances for CTCF, RAD21, SMC3, and ZNF143 used to predict boundary regions. Each model is trained via a “holdout” strategy, in which data from chromosomes {CHR1, CHR2, …, CHRi-1, CHRi+1, …, CHR22} were used to build the model and the ith chromosome was reserved for testing. See for more detail on the model building strategy.
ptairData The package ptairData contains two raw datasets from Proton-Transfer-Reaction Time-of-Flight mass spectrometer acquisitions (PTR-TOF-MS), in the HDF5 format. One from the exhaled air of two volunteer healthy individuals with three replicates, and one from the cell culture headspace from two mycobacteria species and one control (culture medium only) with two replicates. Those datasets are used in the examples and in the vignette of the ptairMS package (PTR-TOF-MS data pre-processing). There are also used to gererate the ptrSet in the ptairMS data : exhaledPtrset and mycobacteriaSet
scpdata.
SimBenchData The SimBenchData package contains a total of 35 single-cell RNA-seq datasets covering a wide range of data characteristics, including major sequencing protocols, multiple tissue types, and both human and mouse sources.
SingleMoleculeFootprintingData This Data package contains data objcets relevanat for the SingleMoleculeFootprinting package. More specifically, it contains one example of aligned sequencing data (.bam & .bai) necessary to run the SingleMoleculeFootprinting vignette. Additionally, we provide data that are essential for some functions to work correctly such as BaitCapture() and SampleCorrelation().
STexampleData Collection of spatially resolved transcriptomics datasets in SpatialExperiment Bioconductor format, for use in examples, demonstrations, tutorials, and other purposes. The datasets have been sourced from various publicly available sources, and cover several technological platforms.
TENxVisiumData Collection of Visium spatial gene expression datasets by 10X Genomics, formatted into objects of class SpatialExperiment. Data cover various organisms and tissues, and include: single- and multi-section experiments, as well as single sections subjected to both whole transcriptome and targeted panel analysis. Datasets may be used for testing of and as examples in packages, for tutorials and workflow demonstrations, or similar purposes.
There are 7 new annotation packages in this release of Bioconductor.
AHLRBaseDbs Supplies AnnotationHub with
LRbaseDb
Ligand-Receptor annotation databases for many species. All the SQLite files
are generated by our Snakemake workflow
lrbase-workflow. For the
details, see the README.md of lrbase-workflow.
AHMeSHDbs Supplies AnnotationHub with
MeSHDb NIH MeSH
annotation databases for many species. All the SQLite files and metadata.csv
are generated by our Snakemake workflow
mesh-workflow.
AHPathbankD.
AHPubMedDbs Supplies AnnotationHub with some preprocessed sqlite, tibble, and data.table datasets of PubMed. All the datasets are generated by our Snakemake workflow pubmed-workflow. For the details, see the README.md of pubmed-workflow.
gwascatData This package manages a text file in cloud with March 30 2021 snapshot of EBI/EMBL GWAS catalog.This simplifies access to a snapshot of EBI GWASCAT. More current images can be obtained using the gwascat package.
MafH5.gnomAD.v3.1.1.GRCh38 Store minor allele frequency data from the Genome Aggregation Database (gnomAD version 3.1.1) for the human genome version GRCh38.
Orthology.eg.db Orthology mapping package, based on data from NCBI, using NCBI Gene IDs and Taxonomy IDs.
There is 1 new workflow package in this release of Bioconductor.
There are no new online books.
Changes in version 1.9.3 (2021-01-28)
Now defaulting to exclude sex chromosomes from model fitting
Also included sgc argument in twosamplecompare
Data frame output of ACEcall and twosamplecompare are now restricted to selected chromosomes
Changes in version 1.9.1 (2021-01-15)
accommodating fitting of chromosomes with only a single germline copy (e.g. X and Y in males)
added the option to specify which cellularities to include in squaremodel
option to save readCounts-object in runACE
Changes in version 0.0.99
Changes in version 3.1.5
Removed warning about future_options deprecation
Changes in version 3.1.4
bug fix loading bruker files
Changes in version 3.1.3 (2020-11-19)
nmr_pca_outliers_plot modified to show names in all boundaries of the plot
Changes in version 3.1.2 (2020-11-04)
Bug fix related with Bioconductor Renviron variable R_CHECK_LENGTH_1_CONDITION
Changes in version 3.1.1 (2020-10-30)
Modified order of autor list
Changes in version 3.1.0 (2020-10-22)
Changes in version 1.1.5 (2021-03-09)
Bugs fix: fix the bug of inflated p-values and inconsistent output formats.
Changes in version 1.1.4 (2021-02-28)
Bug fix: fix the bug when metadata contains only a single variable and some samples were removed with the minimum library size cutoff.
Changes in version 1.1.3 (2021-02-19)
Add a warning message for the case of the small number of taxa.
Changes in version 1.1.2 (2020-12-08)
Bug fix: fix the bug that the sampling fraction estimate will return a single number instead of a vector.
Changes in version 1.1.1 (2020-11-20)
Integrating with functions from the microbiome package.
Changes in version 1.54.0
NEW FEATURES
There is a new replacement package for the Inparanoid orthology packages, called Orthology.eg.db
This package uses NCBI orthology data to map NCBI Gene IDs between species using the usual select() interface
MODIFICATIONS
UniGene data have been removed from OrgDb and ChipDb packages
Gene type data have been added to OrgDb and ChipDb packages
Changes in version 1.53.0
NEW FEATURES
MODIFICATIONS
Changes in version 1.34.0
NEW FEATURES
Removed UniGene from OrgDb and ChipDb packages
Added Gene Type table to OrgDb and ChipDb packages
Added functionality to build Orthology.eg.db package which maps NCBI Gene IDs between species
RSQLite deprecated usage of dbGetQuery for database altering statements; updated to use dbExecute instead
Changes in version 2.99.0
MAJOR UPDATES
.
(2.99.0) Another major change, a default caching location is automatically created in a non interactive session instead of using a temporary location. In an interactive session, a user is still prompted for permission.
Changes in version 2.23.0
USER-VISIBLE MODIFICATIONS
MODIFICATIONS
Changes in version 1.21.0
MODIFICATIONS
1.21.9 Add PNG as valid source type
1.21.4 Removed vignette for creating annotation hub package. Reference and refer to single vignette in AnnotationHub
1.21.3 Tags for database now combination of biocViews and meta$Tags. Also checks for valid AnnotationHub or AnnotationHubSoftware biocViews.
1.21.2 Add mtx.gz as valid source type
BUG CORRECTION
INTERNAL BUG CORRECTION
REMOVED
Changes in version 1.4.0
NEW FEATURES
(v 1.3.1) support Rawls() service (more fine-grained implementation / extension of the ‘Terra()’ orchestration API).
(v 1.3.2) introduce avworkspace_*() functions for viewing and updating workflow configurations.
(v 1.3.3) introduce avnotebooks_() functions for managing notebooks on workspaces and runtimes.
(v 1.3.11) introduce avtable_paged() for page-wise access to tables
(v 1.3.14) introduce avworkspace_clone() for cloning existing workspaces.
(v 1.3.21) avworkspaces() returns a tibble of available workspaces.
(v 1.3.24) gsutil_rsync() supports a regular expresion exclude = to exclude files from synchronization.
(v 1.3.24) avworkflow_localize() copies workflow control and / or output files to the local disk.
USER VISIBLE CHANGES
(v 1.3.1) service functions have signatures like fun(x, …, .body = list(y)), where x is a argument for the ‘URL’ of the RESTful interface, and y is an argument for the ‘BODY’ of POST and similar requests. The … provide backward compatibility, and is used to populate elements of .body; the full interface is required when URL and BODY have identically named arguments.
(v 1.3.10, 1.3.11) return ‘entity’ column with name ‘table_id’, rather than ‘name’.
(v 1.3.22) localize() / delocalize() warn when dry = TRUE, so that lack of localization is more apparent.
(v 1.3.24) gsutil_stat() returns a tibble summaring bucket status, rather than character().
(v 1.3.30) Add Referer: header to all Leonardo requests
BUG FIXES
(v 1.3.6) when .body consists of 1 argument, it is represented as an unnamed set.
(v 1.3.7) allow positional matching for .body arguments
(v. 1.2.1 / 1.3.31) drs_stat() returns a single record per URL when multiple hashes available.
Changes in version 1.2.0
New Features
Bug Fixes
Changes in version 1.5.5 (2021-01-31)
Added ThreeMostPairBam to support paired-end bam.
Changes in version 1.5.4 (2021-01-10)
Fixed the bug in PASEXP_3UTR.
Changes in version 1.5.3 (2021-01-05)
Updated the link of PolyA_DB.
Changes in version 1.5.1 (2020-12-07)
Updated Imports and authors.
Changes in version 1.8.4 (2021-05-12)
R > v4.0.0 is now required
Update documentation & vignette
Code cleaning
Changes in version 1.8.3 (2021-04-05)
artmsProtein2SiteConversion now supports uniprot id isoforms (thanks Emily King)
Update vignette to make clearer how to provide several protein ids in “normalization_reference” (thanks Olga Schubert)
Changes in version 1.8.2 (2021-03-18)
artmsProtein2SiteConversion: New PTM available as argument, a new
user defined
PTM:XXX:yy. Check documentation to find out more
QC plots: by default, all qc plots are now output to a folder directory, by type (qc-basic, qc-extended, qc_summary)
artMS working directory: artMS will create all the folders and subfolders relative to the working directory. No need to specify the full path to the working directory, but the user must set the working directory: setwd(“/path/to/working/directory/”)
Configuration file data object updates:
“output” the user can add a folder where would like to have the output results file. For example, “output: results_202003/example-results.txt” would create the “resutls_202003” folder (if it does not exist) with all the results files available there
“LFC” (log2fc) updated to range -0.58 to 0.58, i.e., a fold change larger than a 1.5 (instead of 2 as before)
Update and improve documentation and vignette
Several bug fixes
Changes in version 1.8.1 (2020-10-27)
Update “plotPCA” message
Update documentation and vignettes
Changes in version 2.1.3
NEW CITATION
ASpli was published on Bioinformatics
FEATURES
BUG FIXES
gbCounts identifies correctly NA in junction’s name
minAnchor in jCounts was hardcoded so it had no impact on analysis. It is being passed correctly now.
Changes in version 2.1
NEW FUNCTIONS AND FUNCTIONALITIES
New locus plot helper function .plotGenePattern.
plots coverage, junctions and architecture
FEATURES
Enhancement to the vignettes.
Quick start section was modify in order to use gtf and bam files provided by ASpli package
Add new section ASpli overview in vignette
BUG FIXES
binGenome function assigns correctly bins located at the start and the end of each gene
binGenome function calculates correctly gene range overlap
Changes in version 1.15.11
Break the limitation of sequence length must have ends less than or equal to 536870912.
Changes in version 1.15.10
fix the issue that idxstatsBam return values with “*”
Changes in version 1.15.9
Add rmarkdown as suggest package.
Changes in version 1.15.8
update documentation for the case when no BSgenome object is available.
Changes in version 1.15.7
fix the NA values for TSSEscore when infinite value is in the data.
Changes in version 1.15.6
fix the missing link of documentation for rtracklyaer:import.
Changes in version 1.15.5
remove duplicates when shift reads.
Changes in version 1.15.4
Fix the issue when empty object input into exportBamFile.
Changes in version 1.15.3
Reuse header when exportBamFile in splitGAlignmentsByCut function.
Changes in version 1.15.2
Fix the tag MC in exportBamFile function.
Changes in version 1.15.1
write exportBamFile function to replace rtracklayer::export.bam.
Changes in version 1.13
Changes in version 0.99.0 (2020-08-05)
Changes in version 0.99.1
NEW FEATURES
SIGNIFICANT USER-VISIBLE CHANGES
BUG FIXES
None.
Changes in version 0.99.0
NEW FEATURES
SIGNIFICANT USER-VISIBLE CHANGES
BUG FIXES
Changes in version 0.99.0 (2021-02-22)
Changes in version 2.3.4 (2021-04-18)
Add missing import from scran
Changes in version 2.3.3 (2021-04-14)
Version bump to trigger new build
Changes in version 2.3.2 (2021-04-14)
Bug fixes in handling of divide and conquer inference.
Changes in version 2.3.1 (2020-12-14)
scaling of
mu.mu in
.EmpiricalBayesMu to match the scale given by
spike-ins
scaling of
mu0 in
.BASiCS_MCMC_Start to match the scale given by
spike-ins
when using an EB prior for mu
lower minimum tolerance
mintol_mu (1e-5 instead of 1e-3) as a
default value
in
.BASiCS_MCMC_ExtraArgs
Changes in version 1.4.0
Support installation from Python package directories on the file system.
Clean Conda package directories during a system installation to reduce disk usage.
Changes in version 1.4.0
Avoid caching the installer when performing a system installation in installConda(). Otherwise, cache in the external directory to avoid requiring/polluting BiocFileCache’s cache.
Officially give up on Windows 32-bit support in installConda().
Migrated activateEnvironment() back here, from basilisk.
Added cleanConda() utility to clean the Conda environment.
Added setCondaPackageDir() to set the Conda package cache directory.
Changes in version 1.8.0
Migrate findMutualNN() to BiocNeighbors.
Support d=NA in multiBatchPCA() for more convenient disabling of PCA in calling functions.
Bugfix for d=NA with specified subset.row= in fastMNN().
Added the applyMultiSCE() function to easily apply functions across main/alternative Experiments from multiple SingleCellExperiment inputs.
Added the mnnDeltaVariance() function to compute diagnostics from the variances of the differences between MNN pairs.
Added the quickCorrect() function to quickly perform intersection, normalization, feature selection and correction.
Added some clustering-based diagnostics (clusterAbundanceVar(), clusterAbundanceTest() and compareMergedClusters()) from the OSCA book.
File-backed matrices are now realized into memory prior to multiBatchPCA().
Changes in version 1.1.3
Minor improvements and fixes
getRDS() updated with new URL.
Changes in version 1.1.2
Minor improvements and fixes
clusterPlot() accepts character vectors and factors as arguments to label.
Changes in version 1.1.1
Minor improvements and fixes
spatialPreprocess() uses exact rather than approximate PCA by default.
Changes in version 1.1.0
New Bioconductor devel (3.13)
Changes in version 2.8.0
Improve the efficiency of sparse row subsetting in non-DelayedArray rowBlockApply().
Avoid overhead of DelayedArray block processing when DelayedArray is pristine and the type is supported.
Migrated whichNonZero() from scuttle.
Added toCsparse() to make it easier to convert SparseArraySeeds to CsparseMatrixes.
Added realizeFileBackedMatrix() to, well, realize a DelayedMatrix with file-backed components.
Changes in version 2.7.1 (2020-11-03)
Changes in version 1.7.3
Add approaches based on pValue and qValue to generate present/absent calls
Default approach to generate calls is pValue
Add function
merging_libraries allowing to merge calls
per condition
Changes in version 1.27
BUG FIX
(1.27.17) Update support site watched tags. tags are case insensitive
(1.27.15) Reporting checking of vignette despite package type (@lshep, #136)
(1.27.9) Allow portability of child Rmd documents via parseFile
(1.27.3) Correct check for if package already exists in CRAN/Bioc
(1.27.3) Correct check for single colon use
(1.27.2) Correct path to R license database file by calling R.home(‘share’).
NEW FEATURES
(1.27.16) Check vignettes for all package types (@lshep, #136)
(1.27.12) Check for
LazyData: TRUE in the DESCRIPTION (@lshep,
#128)
(1.27.11) R version dependency check in the ‘DESCRIPTION’ is now a ‘NOTE’ (@lshep, #126)
(1.27.10) Check for ‘error’ and other keywords in signaler functions, ‘message’, ‘warning’, and ‘stop’ etc. (@hpages, #125)
(1.27.8) Check for ‘tests’ entry in ‘.Rbuildignore’
(1.27.7) Removed BiocCheck and BiocCheckGitClone installation
scripts;
recommended usage is
BiocCheck()
(1.27.6) Check that a user has the package name in watched tags of support site
(1.27.5) Check for ‘paste’ / ‘paste0’ in signaler functions, ‘message’, ‘warning’, and ‘stop’ (@LiNk-NY, #64)
(1.27.4) Check for downloads from external resources (github, gitlab, bitbucket, dropbox; @LiNk-NY, #75)
(1.27.1) Check that licenses do not exclude classes of users, e.g., non-academic users.
Changes in version 1.99.
(1.99.0) An enviornment variable may be set system wide or user wide to control the default caching location: BFC_CACHE. Note: do not use R variables or command line export to set this variable. It must be set system wide or user wide for reproducibility in future R sessions or else it must be specified upon ever usage. It must be set before calling library(BiocFileCache) to take effect.
(1.99.0) Fixes partial argument matching error in SQL function SQLExecute
(1.15.1) Added file locking for thread-safe SQL operations. Thanks for the PR @LTLA
BUG FIX
Changes in version 1.10.0
Migrated findMutualNN() from batchelor.
Vendored the RcppAnnoy headers for greater reproducibility.
Added a distance=”Cosine” option for all algorithms.
Changes in version 1.26
USER VISIBLE CHANGES
Changes in version 1.10.0
NEW FEATURES
biocPkgRanges allows for easy identification of package statuses
from
the build report for a specified range of packages (ordered
alphabetically)
biocBuildEmail provides core-team functionality for sending email
notifications to package maintainers
SIGNIFICANT USER-VISIBLE CHANGES
biocBuildEmail allows for saving a credentials file for email
authentication via the
credFile argument
setCache uses
tools::R_user_dir("BiocPkgTools", "cache") instead
of
rappdirs::user_cache_dir
BUG FIXES
biocBuildReport accounts for some packages whose
DESCRIPTION file
is
malformed
biocBuildReport updated to changes in the build report format
Changes in version 2.20.0
Changes in version 1.1.10
NEW FEATURES
Added the function use_bioc_coc() as requested by Luke Zappia et al.
Changes in version 1.1.9
NEW FEATURES
Now use_bioc_github_action() has a docker argument which controls whether to build a docker image at the end of the GHA workflow (only on Linux) as requested by Kévin Rue-Albrecht.
Changes in version 1.1.7
BUG FIXES
Switch to match usethis 2.0.1 which changed a lot of the internal code in biocthis.
Changes in version 1.1.4
NEW FEATURES
Switched from knitcitations to RefManageR given the discussion at.
Changes in version 1.1.3
BUG FIXES
Changes in version 1.59.0
ENHANCEMENT
(1.57.3) Add biocViews term DifferentialDNA3DStructure
(1.57.2) Add CRAN packages to reverse dependency list
(1.57.1) Add biocViews term Chlamydomonas_reinhardtii
Changes in version 0.99.11 (2021-05-17)
Change example inside BiodbConfig to avoid misinterpretation of
set('cache.directory', '~/my.biodb.cache'), leading to believe that
some files are written inside USER HOME folder when running the
example.
Changes in version 0.99.10 (2021-05-07)
Correct documentation of C++ function.
Changes in version 0.99.9 (2021-05-07)
Solving some NOTES from BiocCheck.
Correct example in Progress class.
Changes in version 0.99.8 (2021-05-06)
Correct template travis.yml for extensions: missing deps install, run all checks.
Improve template Makefile for extensions.
Add missing test-cpp.R template file for running C++ tests from testthat.
Limit by default the entries to test to one entry inside generic tests.
Improve vignettes.
Rename default vignette into “biodb.Rmd”.
Changes in version 0.99.7 (2021-04-27)
Renamed Biodb class into BiodbMain in order to avoid “Rd warning: Previous alias or file overwritten by alias: biodb” on Windows platform.
Implement newInst() global function for creating new BiodbMain instance.
Changes in version 0.99.6 (2021-04-27)
Rebuilding doc.
Changes in version 0.99.5 (2021-04-27)
Add missing parameters documentation for runGenericTests().
Changes in version 0.99.4 (2021-04-27)
Move long tests to separate directory “long”.
Changes in version 0.99.3 (2021-04-27)
Added “biodb” as watched tag on my profile on support site.
Changes in version 0.99.2 (2021-04-27)
Switch to MassBank extract for testing MassCsvFile and MassSqlite connectors.
Changes in version 0.99.1 (2021-04-26)
Remove Git files refused by BiocCheckGitClone.
Use CHECK_RENVIRON in local tests.
Correct condition in BiodbEntryFields::getRealName() that did not pass check.
Add all doc files man/*.Rd for BiocCheck run on.
Changes in version 0.99.0 (2021-04-22)
Submitted to Bioconductor
Changes in version 2.48.0
NEW FEATURES
getSequence() now allows the cache to be turned off via the ‘useCache’ argument.
Automatic detection of SSL issues with Ensembl, and appropriate settings applied to httr functions used by biomaRt.
BUG FIXES
Addressed issue with getSequence() and ID types that are not available on the ‘sequences’ page. This could result in truncated sequences being returned from a query.
getBM() would fail if it found a cache entry, but the file was corrupted. Invalid entries are now detected and deleted if encountered.
Changes in version 0.99.0 (2021-03-05)
Changes in version 1.19.2
MINOR MODIFICATION
Changes in version 0.99.38
Changes in version 1.2.0
Previously zero-weight edges are now assigned a nominal positive weight in makeSNNGraph().
Added MbkmeansParam() to wrap mini-batch k-means from mbkmeans.
Added SOMParam() to wrap self-organizing map implementation from kohonen.
Added AffinityParam() to wrap the affinity propagation code from apcluster.
Added DbscanParam() to provide a custom DBSCAN implementation with automatic eps choice.
Added PamParam() to wrap the PAM implementation from cluster.
Added ClaraParam() to wrap the CLARA implementation from cluster.
Added AgnesParam() to wrap the agglomerative nesting method from cluster.
Added DianaParam() to wrap the divisive analysis method from cluster.
Added clusterSweep() to easily perform parameter sweeps via clusterRows().
Added linkClusters() to find relationships between clusters in different clusterings.
Added compareClusterings() to compute similarities between multiple clusterings.
Added nestedClusters() to quantify the degree of nesting across two clusterings.
Moved objects into objects$kmeans for KmeansParam() when full=TRUE.
Moved objects into objects$hclust for HclustParam() when full=TRUE.
Added clusterRMSD() to compute the root-mean-squared-deviation for each cluster.
Changes in version 2.1.2
BUG FIXES
Changes in version 1.5.2 (2020-12-04)
Changes in version 1.34.0
BUG FIXES
Reform the CTSS class. New accessor:
CTSS() (with no dot).
Correct a class error when loading BAM files. (Closes #36).
Use the BSgenome object from the main environment if available.
Changes in version 1.47.1
BUG FIXES
Changes in version 2.1.0
Changes in version 1.14.0 (2021-04-28)
New Features
Heatmaps can now be stored as PDF files.
Functions now show shorter and more clearer messages.
Package no longer requires Java Runtime Environment for storing excel files and it is compatible with older 32 bit operating systems.
log z-scores provided by cgdsr are used instead of z-scores.
Changes in version 2.4.0
New features
Bug fixes and minor improvements
Changes in version 0.1.1
New features
Improved usability by changing descriptions and adding interactive tours
Changes in version 0.1.0
New features
much of the functionality available, in a proof of concept format.
Changes in version 0.0.1
New features
Changes in version 1.7.7 (2021-04-12)
Added handling for sparse matrices
Changes in version 1.7.6 (2021-04-04)
Added functions for creating HTML reports
Fixed bug in decontX plotting
Changes in version 1.7.4 (2021-03-09)
Enable input of raw/droplet matrix into decontX to estimate ambient RNA
Changes in version 0.99.0
Changes in version 0.99.11 (2021-05-11)
Bug fixes and documentation update for Bioconductor release
Changes in version 0.99.0 (2020-09-02)
Changes in version 2.16.0
Changes in version 3.25.6
Fix a bug in estLibSize introduced by last push.
Changes in version 3.25.5
Add LazyDataCompression in description
Changes in version 3.25.4
Add choice endMinusStart to annotatePeakInBatch.
Changes in version 3.25.3
fix the missing link of documentation for rtracklyaer:import.
Changes in version 3.25.2
update documentation.
update findEnhancers to for known interaction data
Changes in version 3.25.1
fix the bug for genomicElementDistribution when the peak length is zero.
Changes in version 1.27.4
Changes in version 1.27.3
Changes in version 1.27.2
Changes in version 1.27.1
Changes in version 1.1.3
Major Changes
Support “multi-feature” analysis, e.g. parallel analysis of multiple features (bins, peaks or gene) on the same object.
New “Coverage” tab & functions generate_coverage_tracks() and plot_coverage_BigWig() to generate cluster coverage tracks and interactively visualise loci/genes of interest in the application.
New inter- and intra-correlation violin plots to vizualise cell correlation distribution between and within clusters.
New normalization method : TF-IDF combined with systematic removal of PC1 strongly correlated with library size.
Simple ‘Copy Number Alteration’ approximation & visualization using ‘calculate_CNA’ function for genetically re-arranged samples, provided one or more control samples.
New generate_analysis() & generate_report() functions to run a full-on ChromSCape analysis and/or generate an HTML interactive report of an existing analysis.
Supports ‘custom’ differential analysis to find differential loci between a subset of samples and/or clusters.
New pathway overlay on UMAP to visualize cumulative pathways signal directly on cells.
Now supports ‘Fragment Files’ input (e.g. from 10X cell ranger scATAC pipeline), using a wrapper around ‘Signac’ package FeatureMatrix() function.
New ‘Contribution to PCA’ plots showing most contributing features and chromosome to PCA.
Restructuration of the ChromSCape directory & faster reading/saving of S4 objects using package ‘qs’.
Minor Changes
RAM optimisation & faster pearson cell-to-cell correlations with ‘coop’ package, and use of ‘Rcpp’ for as_dist() RAM-efficient distance calculation.
Faster correlation filtering using multi-parallel processing.
plot_reduced_dim now supports gene input to color cells by gene signal.
All plots can now be saved in High Quality PDF files.
Changed ‘geneTSS’ to ‘genebody’ with promoter extension to better reflect the fact that mark spread in genebodies.
Possibility to rename samples in the application.
Downsampling of UMAPs & Heatmaps for fluider navigation.
Changed ‘total cell percent based’ feature selection to manual selection of top-covered features, as the previous was srongly dependent on the experiment size.
Faster sparse SVD calculation.
Faster differential analysis using pairWise Wilcoxon rank test from ‘scran’ package.
Changes in version 0.99.0
Overview:
New functionalities:
Input dataset read an creation
CIMICE analysis and CPMC inference
Output data visualization
Changes in version 1.5.3
Changes in version 1.29.1
Changes in version 3.99.1
Add new data set, DE_GSE8057, which contains DE genes obtained from GSE8057 (2020-03-08, Mon)
Changes in version 3.99.0
Add KEGG enrichment analysis of Human Gut Microbiome data (2021-02-20, Sat)
Changes in version 3.19.1
Changes in version 1.3.3 (2021-02-28)
Launch shiny app with
run_clustifyr_app()
Plot and GO for most divergent ranks in correlation of query vs reference
Changes in version 1.3.2 (2021-02-25)
build_atlas() for combining references
More Q&A
Changes in version 1.3.1 (2020-12-26)
Q&A section
Now defaults to top 1000 variable genes in Seurat (including v4)
Bug fixes
Changes in version 1.5.2
SIGNIFICANT USER-VISIBLE CHANGES
loadCNVcalls() does not check cnvs.file names by default when loading (read.csv()) the cnvs.file
loadCNVcalls() allows optional check.names.cnvs.file parameter
Vignette updated
MINOR
Added rmarkdown to Suggets in DESCRIPTION file
Changes in version 1.5.1
BUG FIXES
SIGNIFICANT USER-VISIBLE CHANGES
plotVariantsForCNV() allows two new parameters for customize legend visualization
plotAllCNVs() allows ‘genome’ parameter to work with different genomes
MINOR
Minor vignette fixes
Other minor fixes
Changes in version 0.99.3 (2021-04-14) 1.23.1 (2021-05-16)
Changes in version 2.7.10
anno_simple(): text symbols can have nchar > 1.
anno_text(): add
show_name argument.
Changes in version 2.7.9
add
frequencyHeatmap().
add
Heatmap3D().
Changes in version 2.7.8
add
cluster_between_groups().
add
graphics argument in
anno_block().
Changes in version 2.7.7
discrete numeric legend labels are in correct order now.
parallel is implemented with foreach + doParallel
expression is properly processed for discrete legends
adjust_dend_by_x(): simplified the representation of units.
number of split can be the same as number of matrix rows/columns.
Changes in version 2.7.6
Legend(): add a new argument
grob.
Changes in version 2.7.5
anno_block(): add
labels_offset and
labels_just.
anno_lines():
show_points can be a vector.
pheatmap(): support
kmeans_k.
Changes in version 2.7.4
add
save_last option in
ht_opt().
Changes in version 2.7.1
normalize_comb_mat(): add
full_comb_sets and
complement_set
arguments to control
full sets of combination sets.
adjust the space of column title according to ggplot2.
Legend(): for title_position == “lefttop”, the title position is
adjusted.
Legends are automatically adjusted according to the device size when resizing the device.
Legend(): add
interval_dist to control the distance of two
neighbouring breaks.
Fixed a bug that it crashes Rstudio
make_comb_mat(): print warning messages when there are NA values in
the matrix.
temporary solution for woking under retina display with Rstudio
add
bin_genome() and
normalize_genomic_signals_to_bins()
print messages if directly sending
anno_*() functions to
top_annotation or similar arguments.
pheatmap(): set heatmap name to “ “ so that there is no legend
title by default.
also translate
stats::heatmap() and
gplots::heatmap.2().
move all code for interactive heatmap to InteractiveComplexHeatmap package.
Changes in version 0.99.0
Changes in version 0.99.343 (2021-04-09)
Submission to Bioconductor
NAMESPACE
Exported new function conclusCacheClear()
DESCRIPTION
Removed LazyData: true.
DataFormatting.R
Updated documentation
loadDataset.R
Simplified nested “if” in loadDataset.R
methods-normalization.R
Modified the use of getBM to retrieve only genes of the count matrix (instead of the all database)
test_setters.R/test_getters.R
Simplified nested “if” in loadDataset.R
test_loadData.R
Adapted the unit tests to the new format of coldata and rowdata
test_scRNAseq-methods.R
Used tempdir() for output directory
inst
New data generated
vignette
Changes in version 0.99.0 (2021-03-01)
Changes in version 0.99.6
Update vignette: add MA plotting and DEA sections, and example of bad MA plot
Changes in version 0.99.5
depends: R4.1
updated BugReports link
Changes in version 0.99.4
negative input values are not allowed
warn and automatically replace zero input values by NA
bugfix in warning message formatting
Changes in version 0.99.3
bugfix in float specification of warning message
Changes in version 0.99.2
bugfix remove stray Rproj file
Changes in version 0.99.1
bugfix in documentation examples
Changes in version 0.99.0
initial release
Changes in version 0.99.2
Changes in version 1.26.0
filterWindowsGlobal() finally behaves correctly for variable-width data=.
normFactors() and normOffsets() accept DGEList inputs in their object= and se.out= arguments.
mergeResults() and friends now default to taking tab= from the mcols() of the inputs.
Changes in version 1.10.0
Improvements to graphical interface functions:
Major changes
Bug fixes and minor changes
Changes in version 1.1.0 (2020-10-02)
Changes in version 0.99.0 (2021-02-19)
Changes in version 1.3.6 (2021-04-23)
scaleImages accepts numeric vector value
Changes in version 1.3.5 (2021-04-07)
Added measureObjects function
Changes in version 1.3.4 (2021-03-20)
Support on disk representation of images
Changes in version 1.3.3 (2021-01-24)
Added snapshot tests for shiny
Support win32 again
Changes in version 1.3.2 (2021-01-12)
Updated citation
Changes in version 1.3.1 (2020-12-01)
Allow thick border contours.29.1
Changes in version 1.3.1
change cmdscale.out for eigen.vectors in methyl_MDS_plot
Changes in version 1.3.0
update with new Bioc version
Changes in version 0.99.0 (2021-01-25)
Changes in version 2.7.3 (2021-04-01)
Fix: changed example for adjustSignaturesForRegionSet() to limit memory usage (previous example produced error during check on Windows for arch ‘i386’).
Fix: made sure that the extension of genomic regions by half the sequence pattern (needed for the adjustSignaturesForRegionSet() function) does not result in out-of-bounds regions.
Changes in version 2.7.2 (2021-03-26)
Updated readAlexandrovSignatures() to read the COMSIC signature format v3.2 (published in March 2021).
Changes in version 2.7.1 (2021-03-21)
Updated readAlexandrovSignatures() to add the possibility to read COSMIC signatures of version 3.1 directly from an Excel file (as provided on the COSMIC website).
Added possibility to adjust/normalize mutational signatures to specific subsets of the human genome (defined by means of GRanges objects). The adjustment/normalization is performed accoring to the nucleotide frequencies in the specified regions (with respect to nucleotide frequncies in the reference sequences, e.g., the whole genome, for which the signatures were derived in the first place).
Changes in version 0.99.0
New features
Methods
New decouple() integrates the various member functions of the decoupleR statistics for centralized evaluation.
New family decoupleR statists for shared documentation is made up of:
Converters
Changes in version 0.99.0 (2021-03-21).27.1
Changes in version 0.18.0
NEW FEATURES
Implement ConstantArray objects. The ConstantArray class is a DelayedArray subclass to efficiently mimic an array containing a constant value, without actually creating said array in memory.
Add scale() method for DelayedMatrix objects.
Add sinkApply(), a convenience function for walking on a RealizationSink derivative and filling it with blocks of data.
rbind() and cbind() on sparse DelayedArray objects are now fully supported.
Delayed operations of type DelayedUnaryIsoOpWithArgs now preserve sparsity when appropriate.
SIGNIFICANT USER-VISIBLE CHANGES
BUG FIXES
Subsetting of a DelayedArray object now propagates the names/dimnames, even when drop=TRUE and the result has only 1 dimension (issue #78).
log() on a DelayedArray object now handles the ‘base’ argument.
Fix issue in is_sparse() methods for DelayedUnaryIsoOpStack and DelayedNaryIsoOp objects.
cbind()/rbind() no longer coerce supplied objects to type of 1st object (commit f1279e07).
Fix small issue in dim() setter (commit c9488537).
Changes in version 1.14.0
Fix for missing na.rm= argument in AvgsPerSet functions.
DelayedMatrixStats no longer has a hard requirement on HDF5Array or BiocParallel.
Correct handling of drop= by quantile functions (<URL:>).
Fix 2 issues with how the center argument is handled (<URL:>).
Changes in version 1.0.0
Changes in version 1.2.0
Changes in version 1.7.2 (2021-03-25)
Major internal changes to the depeche function, with two user consequences: o The dualDepeche option is deprecated, as it made the function very heavy to maintain and was not flexible enough to be of great use. o The interface to dAllocate is much improved, allowing for smooth allocation of new data to an established model, which makes large dualDepeche runs, constructed outside of the function, possible in a more versatile way than previously.
Changes in version 1.7.1 (2021-02-02)
Adding the option of not scaling the data within the depeche function
Condensing the code for the depeche scaling procedure
Changes in version 1.31.16
Turning off outlier replacement with glmGamPoi fitting.
Changes in version 1.31.15
Added ‘saveCols’ in results() and lfcShrink() to pass metadata columsn to output.
Changes in version 1.31.13
Allow additional arguments to be passed to data-accessing functions in integrateWithSingleCell().
Changes in version 1.31.2
Fixed interface with glmGamPoi so that normalizationFactors can be used. Thanks to Michael Schubert for spotting this and to Constantin Ahlmann-Eltze for pointing out the fix.
Changes in version 1.5.2 (2021-05-05)
Update vignette for dispersion estimation
Changes in version 1.4.2 (2020-09-30)
Fix figure scaling issue in vignette
Changes in version 0.99.0
Changes in version 1.3.18
Using data.table instead of data.frame for modify-in-place.
Added support for Metabolomics DIA data.
Hierarchical clustering based alignment.
Create a child run (features + chromatograms) from two parents.
Added support for sqMass files.
Changes in version 1.3.5
Supporting transition level intensity for SAINTq
Added support for pyopenms.
Added support for sqMass files.
Added parallelization using BiocParallel.
Using context-specific qvalues to determine reference.
Alignment is done over multipeptide instead of multiprecursor.
Precursors of a peptides are forced to have same feature-RT.
Savitzky Golay smoothing in C++.
Fast and light global alignment functions.
Changes in version 3.2
New type of plot: dba.plotProfile()
Can mix single-end and paired-end bam files
Various bug fixes
Changes in version 1.10.2
Added helper functions to compute the exact moments, so that the user can characterise the systematic biases in the diffusion scores
Changes in version 1.10.1
Changes in version 0.99.27 (2021-04-06)
major speed-up or gene-level calculations
fixed bug using the wrong default coefficient with DEXSeq
Changes in version 0.99.13 (2021-03-04)
fixed misnamed variable bug when creating annotation from ensembldb
formatting and renaming changes to conform with Bioc standards
Changes in version 0.99.10 (2021-02-05)
submitted to BioConductor
improvement on limma::diffSplice
differential 3’ UTR usage
Changes in version 1.4
Added 1 new Visualization function: ‘dittoFreqPlot()’.
Added interaction with ‘rowData’ of SE and SCEs via a ‘swap.rownames’ input, e.g. to simplify provision of ‘var’s via symbols vs IDs.
Improved & expanded ‘split.by’ capabilities by: 1- adding them to ‘dittoBarPlot()’, ‘dittoDotPlot()’, and ‘dittoPlotVarsAcrossGroups()’; 2- adding ‘split.adjust’ input to all functions for passing adjudstments to underlying ‘facet_grid()’ and ‘facet_wrap()’ calls; 3- adding ‘split.show.all.others’ input to ‘dittoDimPlot()’ and ‘dittoScatterPlot()’ to allow the full spectrum of points, rather than just points excluded with ‘cells.use’, to be shown as light gray in the background of all facets; 4- Bug fix: splitting now works with labeling of Dim/Scatter plots, with label position calculated per facet, and without affecting facet order.
Improved ‘dittoPlot()’-plotting engine (also effects ‘dittoPlotVarsAcrossGroups()’, and ‘dittoFreqPlot()’) by: for y-axis plotting, 1- extended geom dodging to also work on jitters when ‘color.by’ is used to add subgroupings & 2- added a ‘boxplot.lineweight’ control option; for x-axis / ridge plotting, 1- added an alternative histogram-shaping option (Try ‘ridgeplot.shape = “hist”’) & 2- improved use of white space via a new ‘ridgeplot.ymax.expansion’ input.
Standardized output logic so that ‘do.hover = TRUE’ will lead to plotly conversion even when ‘data.out = TRUE’.
‘dittoHeatmap()’: ‘order.by’ can also now accept multiple gene/metadata names to order by & bug fix: when given an integer vector, that vector will be used directly to set the order of heatmap columns.
‘dittoBarPlot()’: grouping & ‘var’ order control improved via addition of a ‘retain.factor.levels’ input.
Changes in version 3.17.1
Changes in version 1.12.0
Added BPPARAM= to read10xCounts() for parallelized reading of multiple samples.
Gave all the *Ambience() functions better names, and soft-deprecated the current versions.
Added ambientContribSparse() to estimate the ambient contribution under sparsity assumptions.
Added cleanTagCounts() to remove undesirable barcodes from tag count matrices.
Converted all matrix-accepting functions to S4 generics to support SummarizedExperiment inputs.
emptyDrops() will now coerce all DelayedArray inputs into wrapped SparseArraySeeds.
Setting test.ambient=TRUE in emptyDrops() will no longer alter the FDRs compared to test.ambient=FALSE. Added test.ambient=NA to retain back-compatible behavior.
Bugfix for correct use of redefined lower when by.rank= is set in emptyDrops().
Added a constant.ambient=TRUE option to hashedDrops() to better support experiments with very few HTOs.
Changes in version 0.99.0 (2021-01-11)
Changes in version 1.3.01 (2020-11-06)
Dune now accepts multiple metrics
Dune now uses the NMI by default
Changes in version 1.21.2
Changes in version 2.27.1
DESeq dependency removal
Added extra warning about RPKM usage
Removed Defunct functions
Changes in version 3.34.0
New function featureCounts2DGEList() that converts results from Rsubread::featureCounts() to DGELists.
Remove the “ndim” argument of plotMDS.DGEList().
read10X() now counts the number of comment lines in mtx files and skips those lines when reading in the data.
Fix a bug in voomLmFit() whereby zeros were sometimes incorrectly identified due to floating point errors.
The “bcv” method of plotMDS.DGEList() is scheduled to be deprecated in a future release of edgeR.
Changes in version 1.10
added functionality to parse expressions in labels via parseLabels (TRUE/FALSE)
over-rides ggrepel’s new default value for max.overlaps via introduction of maxoverlapsConnectors = 15
user can now specify a direction for connectors via directionConnectors
removed labhjust and labvjust
added pCutoffCol (via Andrea Grioni)
Changes in version 1.2.3
NEW FEATURES
Update vignettes.
This is a major release update for EnMCB package.
We add new options for selecting the correlation methods.
We add mboost algorithm in our ensemble prediction model.
SIGNIFICANT USER-VISIBLE CHANGES
Delete unused data.
Correct the parameters’ names.
BUG FIXES
Changes in version 1.21.1
Changes in version 2.22.0
hierarchicalfor function
getGenesets)
Changes in version 1.11.3
fix bug in gseaplot2(2021-1-28, Thu)
Changes in version 1.11.2
fix showCategory for cnetplot, emapplot, emapplot_cluster when showCategory is a vector of term descriptions
Changes in version 1.11.1
Changes in version 2.15.3
Fix missing declaration of rmarkdown.
Changes in version 2.15.2
Ensure remote gzipped files are handled properly by
ensDbFromGtf.
Changes in version 2.15.1
Add new field canonical_transcript to the gene table reporting the ID of the gene’s canonical transcript.
Changes in version 1.33.0
Changes in version 0.99.0 (2021-04-09)
R>=4.0 for submission
removed unused dependencies
correct work of generateVcfReport (although SNV only)
unmatched reads are at the end of generateBed* output now
compiles and works on Apple Silicon (native ARM64 R)
fully documented methods
fully covered with tests and examples
comprehensive vignettes
Changes in version 0.4.0 (2021-03-08)
going public
CX report now includes only the context present in more than 50% of the reads
generateVcfReport (capable of dealing with SNVs only for now)
added documentation to some of the methods
added several examples
added sample data for amplicon and capture NGS
added some tests based on sample data
README.md
Changes in version 0.3.9 (2021-01-19)
fast C++ CIGAR parser to lay queries in reference space
new method to extract base frequences: generateBaseFreqReport
Changes in version 0.3.7 (2021-01-12)
lots of refactoring again
CX report sub now uses boost::container::flat_map (additional 2x speedup)
removed dplyr as a dependence, whole package uses data.table now
Changes in version 0.3.5 (2021-01-09)
lots of refactoring
new method: preprocessBam() to save time on loading/preprocessing
new C++ sub for CX report with std::map summary (5-10x speedup)
Changes in version 0.3.2 (2021-01-06)
first attempt to stablilize API (generateCytosineReport and generateBedReport)
temporary method for ECDF (generateBedEcdf)
uploaded to GitHub
Changes in version 0.3.1 (2020-01-01)
heavy refactoring, many internal methods added
C++ functions for nearly all bottlenecks (pending fast: cigar, summary, genome loading)
Changes in version 0.2.1 (2020-12-21)
made this second iteration of epialleleR a usable package
Changes in version 0.99.0
First release of epigraHMM.
It is now possible to add normalizing offsets via addOffsets.
epigraHMM now uses hdf5 files to store all intermediate data during computation of the EM algorithm. Intermediate data include window-based HMM and mixture model posterior probabiltiies, and forward-backward probabilities. This change leads to a better memory utilization upon convergece.
Changes in version 1.0.1
Removed ggrepel, rlang, and factoextra dependencies.
Updated Seurat package switch
Switch the way counts are processed by first eliminating rows with 0 expression in the sparse matrix before converting to a full matrix
Changes in version 1.7.5
Minor bug fix for Mac compilation.
Changes in version 1.7.4 (2020-06-01)
Added ‘scale’ parameter to plotMetricsCluster method.
Changes in version 1.7.3 (2020-04-16)
Clusterboot interfaces can be set through ‘cbi’ parameter to quality methods. It takes one the following values: “kmeans”, “clara”, “clara_pam”, “hclust”, “pamk”, “pamk_pam”.
Changes in version 1.7.2 (2020-04-14)
Stability analysis and quality analysis will not stuck in bootstrap.
Changes in version 1.7.1 (2020-04-13)
Clusterboot interfaces can be set through ‘cbi’ parameter to stability methods. It takes one the following values: “kmeans”, “clara”, “clara_pam”, “hclust”, “pamk”, “pamk_pam”.
Changes in version 1.0.0
New Features
Deprecated & Defunct
Changes in version 1.3.7 (2021-03-10)
Parameter
parallel is changed in the exomePeak2() and
exomePeakCalling() functions; the parameter now enables user to
configure specific number of cores used in the parallel computation
(default = 1).
To avoid the potential confusion for the downstream analysis, the
default settings for the parameter
log2FC_cutoff in functions
exomePeak2() and exomePeakCalling() are changed from 1 to 0. The
adjustment should have very little effect on the peak calling result.
The naming of peaks in the output file is now sorted by their genomic order.
A maximum for peak width is added now, which is by default 100*fragment_length. Such a higher bound can significantly improve the results of DRACH motif finding for m6A-Seq.
Changes in version 1.3.5 (2021-02-07)
Improved the grammar and details in the DESCRIPTION file and the vignettes.
When performing the difference analysis using the function exomePeak2(), the sequencing depth of the interactive GLM will be estimated on the background features, which by default are the disjoint regions of the peaks detected on the exons. Tests on real data revealed that the background approach can make the differential methylation directions more in-line with the expectation of the perturbed protein regulator. Previously, the background sequencing depth estimation can only be realized in the multiple-step functions but not in exomePeak2().
Changes in version 1.3.4 (2021-02-05)
The options
consistent_peak,
consistent_log2FC_cutoff,
consistent_fdr_cutoff,
alpha, and
p0 are deprecated from the
functions exomePeak2() and exomePeakCalling(). The consistent_peak
option was implemented to reproduce the consistent peak calling
algorithm in the old package exomePeak, and its performance is
significantly lower than the NB GLM derived methods according to our
recent tests. Hence, the consistency related functionalities are
removed in the later versions of exomePeak2.
Changes in version 1.3.3 (2021-02-03)
Fix the bug of not merging the overlapping exons when the transcript annotation have no overlapping transcripts, this can happen when a very small annotation is provided.
Changes in version 1.99.0.
Changes in version 1.17.0
(1.17.1) Removed vignette for creating annotation hub package. Reference and refer to single vignette in AnnotationHub
Changes in version 1.17.0
MODIFICATIONS
1.17.2 Removed vignette for creating annotation hub package. Reference and refer to single vignette in AnnotationHub
1.17.1 Tags for database now combination of biocViews and meta$Tags. Also checks for valid AnnotationHub or AnnotationHubSoftware biocViews.
BUG CORRECTION
Changes in version 1.1.0 (2021-05-09)
Changes in version 1.3.2
Changes in version 1.19.1
Changes in version 1.3.0 (2020-11-27)
Changes in version 1.5.5 (2021-05-12)
Changed fcoex object to store a dgCMatrix instead of a dataframe for expression and discretized expression.
Removed options of 3+ class multiclass discretize (may lead to backwards incompatibility) as they would be incompatible with better memory handling of dgCMatrix system.
Changes in version 0.99.0 (2021-04-01)
Changes in version 0.99.7 (2021-04-24)
added info to explain example data in README and vignettes
made minor changes to exported function example comments
plotFemap + parameterized several hard-coded variables
Changes in version 0.99.6 (2021-02-24)
Updated package data script paths
Changes in version 0.99.5 (2021-02-24)
Trimmed external data size
Changes in version 0.99.4 (2021-03-24)
updated package datasets (geneSingle, geneDouble, geneMulti)
created 3 vignettes to describe package implementation using each dataset
runFedup + runs analysis on an input list rather than single test vector + fold enrichment calculation evaluates 0 for 0/0 instances + enriched pathways defined as fold enrichment ≥ 1 (instead of > 1)
writeFemap + writes EM-formatted tables for list of fedup results
plotFemap + implements tryCatch() to return NULL if Cytoscape is not running locally
prepInput + new function to prepare input gene list
Changes in version 0.99.3 (2021-02-24)
Updating R version dependency to 4.1
Changes in version 0.99.2 (2021-02-24)
Untracking system files
Changes in version 0.99.1 (2021-02-23)
Version bump
Changes in version 0.99.0 (2021-02-17)
Submitted to Bioconductor
Changes in version 3.26
Changes in version 1.1.2 (2020-11-11)
Fix bugs in keeping extra reads when filtering with minMapBase
Allow skipping filtering with minMapBase
Changes in version 1.8.0
Changes in version 1.21.6
Changes in version 1.29.1
Changes in version 0.99.0 (2020-09-30) 0.99.56
Improvements to the annotate_foods() function.
Changes in version 0.99.41
Added new function named msea to perform GSEA using FOBI.
Changes in version 0.99.38
Addressing Vince Carey (package reviewer from Bioconductor) comments and suggestions.
Changes in version 0.99.35
Added FOBI table in package data.
Changes in version 0.99.29
Fix Bioconductor Single Package Builder errors and warnings:
Use TRUE/FALSE instead of T/F in ora.R
Changes in version 0.99.24
Submitted to Bioconductor!
Changes in version 0.99.18
Added a function called fobi_graph to generate FOBI graphs.
Changes in version 0.99.12
Changes in version 1.2.1
Add merging of external counts
Add publication
Minor bugfixes
Changes in version 1.28.0
NEW FEATURES
new function
exist.gdsn()
new function
is.sparse.gdsn()
UTILITIES
LZ4 updated to v1.9.3 from v1.9.2
XZ is updated to v5.2.5 from v5.2.4
apply.gdsn(): work around with factor variables if less-than-32-bit
integers are stored
a new component ‘is.sparse’ in
objdesp.gdsn()
options(gds.verbose=TRUE) to show additional information
Changes in version 1.26.1
UTILITIES
apply.gdsn()
Changes in version 1.37.0
Changes in version 2.21.5
Added functions to compute variant-specific inflation factors.
Changes in version 2.21.4
Added the option to perform a fast approximation to the score standard error in assocTestSingle. New function nullModelFastScore prepares a null model to be used with this option.
Changes in version 2.21.1
Updated structure of fitNullModel objects. Null model objects
with the previous structure will be automatically updated with
a warning, but you may want to consider rerunning
fitNullModel if you plan to use an older null model with the
current version.
Changes in version 1.4.0
New features
The main function GeneTonic() gains an extra parameter, gtl - this can be used to provided a named list object where a single parameter is passed (e.g. after loading in a single serialized object), while the functionality stays unaltered. The same gtl parameter is also exposed in other functions of the package - see the vignette for some examples, or check the documentation of each specific function. To create this object in a standardized manner, the function GeneTonic_list() is now available.
A new function to perform fuzzy clustering (following the implementation of DAVID) is added - see gs_fuzzyclustering(). It returns a table with additional information on the cluster of genesets and the status of each set in the group.
The ggs_backbone() function can extract the bipartite graph backbone from the Gene-Geneset graph, this can be further explored below the main element in the Gene-Geneset panel. Once the backbone is created, you are one step away from checking out the genes that act as “hubs” in the Gene-Geneset graph, and possibly identify the nodes playing an essential role based on their connectivity.
A new function, signature_volcano(), adds a signature volcano plot to the Gene-Geneset panel. This plot displays the genes of a chosen geneset in color, while the remaining genes of the data are shown as shaded dots in the background. The color and transparency of the displayed genes can be chosen by the user, as well as the option to display the gene names of all genes in the geneset.
gs_summary_overview() can also generate bar plots instead of the default segment-dot (lollipop) plots.
A new function, summarize_ggs_hubgenes(), builds a DT datatable for the Gene-Geneset panel. This table lists the individual genes of the input data and their respective degree in the Gene-Geneset graph. Furthermore, action buttons linking to the NCBI, GeneCards and GTEx databases are included for each gene.
gene_plot() gains the extra labels_display argument to control whether the labels are at all shown; now the display of the labels is also respecting the jitter of the points
Other notes
Changes in version 1.13.3
Changes in version 1.28.0
NEW FEATURES
SIGNIFICANT USER-VISIBLE CHANGES
DEPRECATED AND DEFUNCT
Changes in version 1.44.0
SIGNIFICANT USER-VISIBLE CHANGES
DEPRECATED AND DEFUNCT
Deprecate disjointExons() in favor of exonicParts().
Remove species() method for TxDb objects (was deprecated in BioC 3.3 and defunct in BioC 3.4).
Changes in version 1.5.1
Changes in version 1.44.0
SIGNIFICANT USER-VISIBLE CHANGES
DEPRECATED AND DEFUNCT
Changes in version 2.4.0
USER VISIBLE CHANGES
The gscores() function now returns the SeqInfo from the input GScores object.
Improvements on the shiny web app.
Changes in version 1.0.0
Changes in version 0.99.0
Submitted to Bioconductor
Changes in version 0.6.5
Changes in version 0.99.0 (2021-02-01)
Changes in version 2.5.3
Changes in version 2.5.2
Changes in version 2.5.1
Changes in version 1.1.12
import ggtree to pass BiocCheck. (2021-05-14, Fri)
Changes in version 1.1.11
Changes in version 1.1.10
fix a bug for compute_aes ( This is to support mapping aesthetics (x, not y in aes of geom_fruit) to functions of variables). (2021-05-10, Mon)
Changes in version 1.1.9
support mapping aesthetics (x, not y in aes of geom_fruit) to functions of variables. (2021-05-07, Fri)
Changes in version 1.1.8
update vignettes. (2021-04-25, Sun)
Changes in version 1.1.7
update man and vignettes. (2021-04-06, Tue)
Changes in version 1.1.6
remove axis of first geom_tile of vignettes, since the axis of this layer is meaningless. (2021-02-24, wed)
Changes in version 1.1.5
don’t use svg dev. (2021-02-04, Thu)
Changes in version 1.1.4
specific position method for specific geom method automatically. (2021-01-27, Wed)
Changes in version 1.1.3
support multiple density plot from geom of ggridges. (2020-12-31, Thu) geom_density_ridges, geom_density_ridges2, geom_density_ridges_gradient, geom_ridgeline, geom_ridgeline_gradient.
Changes in version 1.1.2
Changes in version 4.9.1
Changes in version 2.17.1
Changes in version 0.99.0 (2021-03-30)
Changes in version 1.37.1 (2020-05-04)
Removed Biocarta and NCI pathways.
Added WikiPathways pathways.
Updated all pathway data.
Changes in version 1.54
SIGNIFICANT USER-VISIBLE CHANGES
Changes in version 1.40
USER VISIBLE CHANGES
The vignette has been rewritten in R Markdown to produce an HTML vignette page and make it shorter and faster to produce.
Development of a shiny app available through the function ‘igsva()’.
BUG FIXES
Replaced fastmatch::fmatch() by IRanges::match,CharacterList-method after disscussion at to avoid the row names of an input expression matrix being altered by fastmatch::fmatch() adding an attribute.
Fixed wrong call to .mapGeneSetsToFeatures() when gene sets are given in a GeneSetCollection object.
Changes in version 1.20.0
NEW FEATURES
Implement the H5SparseMatrix class and H5SparseMatrix() constructor function. H5SparseMatrix is a DelayedMatrix subclass for representing and operating on an HDF5 sparse matrix stored in CSR/CSC/Yale format.
Implement the H5ADMatrix class and H5ADMatrix() constructor function. H5ADMatrix is a DelayedMatrix subclass for representing and operating on the central matrix of an ‘h5ad’ file, or any matrix in its ‘/layers’ group.
Implement H5File objects. The H5File class provides a formal representation of an HDF5 file (local or remote, including a file stored in an Amazon S3 bucket).
HDF5Array objects now work with files on Amazon S3 (via use of H5File()).
BUG FIXES
Changes in version 2.99.4
Improved label- and axis handling for panels with continuous covariates
Formally deprecated heatmap_2 and heatmap_plus
Refactored to switch to devtools tool chain
Changes in version 1.1.1 (2021-02-19)
Changes in version 0.99.3 (2021-05-14)
Remove build/ folder.
Changes in version 0.99.2 (2021-04-20)
Remove some abundant files.
Changes in version 0.99.1 (2021-04-18)
Remove some abundant files.
Changes in version 0.99.0 (2021-04-10)
The first version 0.99.0 is submitted to Bioconductor
Changes in version 1.28.0
hlaPredict() returns the dosage of HLA alleles when
type=”response+dosage”, and
hlaPredict() returns the best guess and dosages by default
a new option “Pos+Allele” in
hlaPredict(),
hlaGenoCombine(),
hlaGenoSwitchStrand(),
hlaSNPID() and
hlaCheckSNPs() for
matching genotypes
by positions, reference and alternative alleles; it is particularly
useful when
the training and test set are both matched to the same reference
genome,
e.g., 1000 Genomes Project
hlaGDS2Geno() supports SeqArray GDS files
a new option ‘maf’ in
hlaAttrBagging() and
hlaParallelAttrBagging()
‘pos.start’ and ‘pos.end’ are replaced by ‘pos.mid’ in
hlaFlankingSNP() and
hlaGenoSubsetFlank()
new function
hlaAlleleToVCF() for converting the imputed HLA
classical alleles
to a VCF file
Changes in version 1.26.1
the hlaAttrBagging object can be removed in garbage collection
without
calling
hlaClose()
enable internal GPU API
improved multithreaded performance compared with v1.26.0
Changes in version 0.99.14 (2021-04-13)
Fixed bug that prevents passing negative values to .hic files
Changes in version 0.99.13 (2021-03-23)
Added RE-agnostic features into construct_features
Changes in version 0.99.12 (2021-02-19)
Submitted to Bioconductor
Changes in version 1.21.1
Changes in version 1.9
Changes in version 1.33
Changes in version 1.33.2
Changes in version 1.33.1
Changes in version 1.33.0
Changes in version 1.0.4
The first update in response to F1000 comments
Added dating arguments to HPA_data_downloader
Now when you have save_file set to true, the file will be stamped with the date it was downloaded. This allows for reproducible access tot he file you created.
To deal with dated files we now have the arguments
version_date_normal and
version_date cancer, which allows users
to
select which downloaded HPA data they want to use based on the date
of
downloading. The default to “last” which will search for the latest
version of the files in the
save_location
The last addition is
force_download, an argument that will overide
the function’s default usage of the local files in case you want to
download a more recent version of the HPA data.
Change to HPAStainR and by extension shiny_HPAStainR
Added Fisher’s Exact Test to HPAStainR’s main function
Due to the inconsistency that exists in using simulated p-values in
chisq.test the default new test if Fisher’s exact and an argument
test_type has been added so users can pick between the two.
Changed the output of the p-values to numeric instead of a character.
Changes in version 1.0.3 (2021-02-03)
Changed read.table() in HPA_data_downloader.R to data.table’s fread()
Changes in version 1.0.2 (2021-25-20)
Changed section of code crashing due to dplyr update.
Changes in version 1.0.1 (2020-11-20)
testthat() HPA_data_downloader.R failed due to spelling change
HPA changed “unfavourable” to “unfavorable”
The testthat() has been changed to reflect their change
More updates soon after all reviews from F1000 are in
Changes in version 1.31.1
Changes in version 0.99.0 (2021-04-23)
Changes in version 1.16.0
New features
Other notes
Changes in version 1.23.6
code cleaning
Changes in version 1.23.3
fixes a testthat misspelling
Changes in version 1.23.2
tolerance sufficience in cell-subclustering not required for first model refinement test
Changes in version 1.23.1
Changes in version 0.99.7 (2021-05-04)
Increased number of times to try to connect to webresource
Changes in version 0.99.6 (2021-05-04)
Adressed comments from Bioconductor review
included a mro.obo.gz file which can be read without unzipping
Changes in version 0.99.1 (2021-01-01)
Submitted to Bioconductor
Changes in version 1.7.2 (2020-05-05)
New dependencies : RANN, leiden, phyclust
Added new partition method for subclustering that uses the Leiden algorithm based on a K-nn adjacency matrix.
Changed the default subclustering method to leiden which is much faster than the random trees method.
Split Bayesian filtering step in two steps, one that runs the model, and one that applies the filter threshold. This allows updating the threshold without having to rerun the whole model.
Fix what groupings of references the subclustering is done on.
Updated expectations of the internally stored clustering information when plotting references to allow for results obtained with version between ~1.3 and this one to be plotted.
Fix add_to_seurat method to work when no seurat object is provided after the reordering fix.
Fix the random trees subclustering applying a different method of centering to the data between the hclust stored in infercnv_obj@tumors_subclusters$hc and the splits in infercnv_obj@tumors_subclusters$subclusters.
Make denoising step figure only be generated if plot_steps is true. (it is identical to final figure that is plotted based on a different option, making it redundant)
Changes in version 1.1.1 (2020-10-30)
Changes in version 1.99.4
update get_PAscore2.
Changes in version 1.99.3
add rmarkdown as suggests.
Changes in version 1.99.2
fix a bug if utr3 list is empty.
Changes in version 1.99.1
add dontrun for getGCandMappability doc.
Changes in version 1.99.0
merge Haibo’s code.
Changes in version 0.99.10
add
response argument so that the server can only respond to one
event from UI.
Changes in version 0.99.9
output can be floating along with mouse positions.
Changes in version 0.99.8
click and hover won’t conflict with brush.
Changes in version 0.99.7
In the sub-heatmap, it allows to remove rows and columns from the four sides.
Changes in version 0.99.0
Submit to Bioconductor
Changes in version 0.0.0.9000
Changes in version 2.26.0
NEW FEATURES
Add commonColnames() accessor to get or set the character vector of column names present in the individual DataFrames of a SplitDataFrameList object.
Implement unary + and - for AtomicList derivatives.
SIGNIFICANT USER-VISIBLE CHANGES
DEPRECATED AND DEFUNCT
BUG FIXES
Fix unplit() on named List objects.
Fix findOverlapPairs() for missing subject (fixes #35).
quantile() on an AtomicList object always returns a matrix (fixes #33).
Fix which.min()/which.max() for CompressedNumericList objects (fixes #30).
Export startsWith() and endsWith() methods for CharacterList/RleList objects (fixes #26).
Changes in version 0.99.8
Changes in version 1.1.11 (2021-05-11)
NEW FUNCTIONALITY
VISIBLE USER CHANGES
FIXES
Fixed a minor issue in CIS_volcano_plot that caused duplication of some labels if highlighted genes were provided in input
Changes in version 1.1.10 (2021-04-08)
FIXES
IMPROVEMENTS
MINOR
FOR DEVS ONLY
Complete rework of test suite to be compliant to testthat v.3
Changes in version 1.1.9 (2021-02-17)
FIXES
Fixed minor issues in internal functions with absolute file paths & corrected typos
Changes in version 1.1.8 (2020-02-15)
FIXES
Fixed minor issues in internal functions to optimize file system alignment
Changes in version 1.1.7 (2020-02-10)
FIXES
Fixed minor issues in import_association_file when checking parameters
Changes in version 1.1.6 (2020-02-06)
UPGRADES
FIXES
Simplified association file check logic in remove_collisions: now function blocks only if the af doesn’t contain the needed columns
Changes in version 1.1.5 (2020-02-03)
UPGRADES
Updated vignettes and documentation
Changes in version 1.1.4 (2020-11-16)
UPGRADES
General improvements for all widget reports
Changes in version 1.1.3 (2020-11-10)
FIXES
NEW
Added vignette “Using ISAnalytics without RStudio support”
Changes in version 1.1.2 (2020-11-05)
FIXES
Fixed missing restarts for non-blocking widgets
Changes in version 1.1.1 (2020-11-04)
FIXES
IMPORTANT NOTES
Changes in version 2.3.14
Bugfix for assignment of annotation colors in ComplexHeatmapPlot.
Changes in version 2.3.13
Deprecated iSEEOptions in favor of panelDefaults (for construction-time globals) and registerAppOptions (for runtime globals).
Changes in version 2.3.12
Added an .allowableColorByDataChoices generic for downstream panels to control ColorBy*Data choices.
Changes in version 2.3.11
Cleaned up tours for Tables and the ComplexHeatmapPlot.
Changes in version 2.3.10
Bugfix for the RowDotPlot color tour.
Changes in version 2.3.9
Bugfix for ordering of selected columns in ComplexHeatmapPlot.
Changes in version 2.3.8
Use shiny::MockShinySession$new() to simulate Shiny session objects.
Changes in version 2.3.7
Bugfix for missing import of geom_density_2d
Changes in version 2.3.6
Bugfix for graceful deprecation of old parameters in various constructors.
Changes in version 2.3.5
Deprecated ColumnSelectionType and ColumnSelectionSaved (ditto for rows) as all active/saved selections are now transmitted.
Changes in version 2.3.4
Fix wiring of button observer to open vignette.
Changes in version 2.3.3
Edge-case bugfix for correct cleaning of zero-row/column SummarizedExperiments.
Changes in version 2.3.2
Added the cleanDataset() generic to ensure all names in the SummarizedExperiment are present and unique.
Changes in version 2.3.1
Changes in version 1.3.5
Switch to registration for storing DE Panel options, via registerPValuePatterns and related functions.
Changes in version 1.3.4
Support in-memory feature set collections and their statistics via registerFeatureSetCollections.
Changes in version 1.3.3
Redistributed documentation from panel tours to UI-specific tours.
Changes in version 1.3.2
Tour-related patch to fix the builds for the time being.
Changes in version 1.3.1
Changes in version 1.13.07 (2021-05-06)
Update type: minor.
importGTF() and importRdata() was updated to handle the rare cases of mixed stranded and unstranded isoforms (unstanded are now discareded).
addORFfromGTF() was updated to better repport if no or only small number of ORFs were added.
Various maintainance updates.
Changes in version 1.13.06 (2021-04-09)
Update type: minor.
The runtimes repported by isoformSwitchTestDEXSeq() was updated to also consider the number of transcripts analysed.
analyzeORF() was updated to enable analysis with analyzeNovelIsoformORF() when no overlaps were found.
switchPlot was fixed so the alphas argument now work.
Various updates of warning, descriptions and error messages.
extractSequence() was updated to remove the terminal stop codon if it is included in the annoation.
extractSequence() was updated to produce evenly sized files when alsoSplitFastaFile=TRUE.
analysORF no longer allows identification of truncated ORFs.
Changes in version 1.13.05 (2021-01-07)
Update type: Major.
analyseORF was updated with the orfMethod “longest.AnnotatedWhenPossible” a hybrid between “longes” and “longestAnnotated”. See ?analyseORF for details.
importGTF, importRdata and analyseORF was updated to also annoate the source of the ORF annoations. analyzeCPAT and analyzeCPC2 was updated to also changes these if removeNoncodinORFs = TRUE.
To enable better ORF analysis the addORFfromGTF() and analyzeNovelIsoformORF() functions were added to IsoformSwitchAnalyzeR. These should be used instead of analyzeORF(). These function also annotate the source of the ORF annoations. See vignette for description of why these are preferable.
analyseORF() was updated with an additional method for ORF detection: “longest.AnnotatedWhenPossible”.
the getCDS() function and CDSSet class was removed for the user as addORFfromGTF() + analyzeNovelIsoformORF() provides a better way to analyse ORFs.
Downstream functions relying on ORF data now checks that all isoforms have been assessed for ORFs. These are extractSequence(), analyzeSwitchConsequences(), switchPlotTranscript() and switchPlot().
isoformSwitchAnalysisPart1() and isoformSwitchAnalysisPart2() was also updated to support the new ORF annotation scheme.
The usage of isoformSwitchAnalysisPart1() and isoformSwitchAnalysisPart2() was made less complex by removing many arguments passed to sub-functions thereby relying more on default arguments.
importRdata() was updated to import the “refrence gene_ids” instead of StringTie gene_ids (for all annotated genes).
the StringTie annotation rescue in importRdata() was updated to use “refrence gene_ids” instead of “refrence gene_names” thereby fixing problems with closely spaced genes, that have the same gene name, which was merged by StringTie.
importGTF() now also imports ref_gene_id from StringTie gtf to enable the above mentioned updates to importRdata(). If not pressent it will duplicate gene_name instead.
extractGeneExpression() was updated to allow easy output of gene annoation.
isoformToGeneExp() was updated to use rowsum() instead of a tidyverse implementation as it is much faster for large datasets.
The result of importRdata()’s estimateDifferentialGeneRange option now repports the condition names in accordance with the rest of IsoformSwitchAnalyzeR.
Removed mentions of StringTie2 as it has been merged into StringTie.
Documentation and vignette was updated accordingly.
Changes in version 1.13.04 (2020-12-10)
Update type: minor.
Vignette update.
Changes in version 1.13.03 (2020-12-08)
Update type: minor.
Vignette update.
Changes in version 1.13.02 (2020-12-07)
Update type: minor.
Description update.
Update of vignette with regards to running on analysis Gallaxy.
Changes in version 1.13.01 (2020-10-29)
Update type: minor.
Version bump due to Bioconductor release.
Fixed an error in importRdata() that could cause trouble when fixing StringTie annotation. Thanks to @yaccos for identifying the problem.
Fixed an edge-case senario where the estimation of DTU in importRdata() caused an error.
analyseSignalP() was updated to handle cases where no signal peptides were found with a warning instead of an error.
Changes in version 1.19.2
FIX
Add affiliation of GE
Remove funs from dplyr to avoid future errors
Fix column_to_names error when there are rownames
Changes in version 1.26.0
release as part of Bioconductor 3.13
Changes in version 1.25.2
removed ‘register’ from macro in ksort.h in order to avoid warnings on Mac OS
Changes in version 1.25.1
minor fix in MismatchC.cpp
Changes in version 1.25.0
new branch for Bioconductor 3.13 devel
Changes in version 1.4.5 (2021-04-15)
SVA batch effect correction improved
MAD outliers detection fixed
KnowSeq report updated to include the changes of SVA and MAD modifications
Cross-Validation DEGs Extraction implemented Further versions
Incorporation of RUV to batch effect methods
Changes in version 3.48.0
New functionality
Explicitly setting
weights=NULL in a call to lmFit() no
longer over-rides the
weights value found in
object.
Default settings in lmFit() changed from
ndups= and
spacing=1 to
ndups=NULL and
spacing=NULL, although this
doesn’t change function behavior from a user point of view.
A number of improvements to duplicateCorrelation() to make the
results more robust and to make the interface consistent with
lmFit(). duplicateCorrelation() sets
weights same as
lmFit(). Setting
weights=NULL in the function call no longer
overwrites weights found in
object. duplicateCorrelation()
now checks whether the block factor is spanned by the design
matrix. If so, it returns intrablock correlations of zero with
a warning. Previously this usage error was not specifically
trapped and could lead to correlations that were or NA or close
to 1 depending on floating point errors.
duplicateCorrelation() now issues a simplified message when
design is not of full rank and uses message() to do so instead
of cat(). In terms of output, duplicateCorrelation() now
bounds the genewise correlations away from the upper and lower
bounds by 0.01 so that the correlation matrix will always be
positive-definite. There is also a fix to the value returned
by duplicateCorrelation() when no blocks or duplicates are
present.
New argument
fc for treat() so that the fold-change threshold
can optionally be specified on the fold-change scale rather
than as a log2-fold-change.
plotMDS() no longer calls cmdscale() but instead performs the
necessary eigenvector computations directly. Proportion of
variance explained by each dimension is now computed and is
optionally added to the dimension labels. The
ndim argument
is now removed. All eigenvectors are now stored so that
plotMDS.MDS does not need to recompute them when different
dimensions are plotted.
New arguments
path and
bgxpath for read.idat().
read.idat() now checks for gzipped IDAT files and, if detected,
gives an informative error message. read.idat() now checks for
existence of input files before calling illuminaio read
functions.
Other code improvements
Documentation
Additional documentation for the
design argument of
lmFit
using the term “samples” instead of “arrays” and mentioning
that the design matrix defaults to
object$design when that
component is not NULL.
duplicateCorrelation() help page revised including new code example.
Help page for voom() now explains that the design matrix will
be set from the
group factor of the DGEList object if
available.
coolmap() help page now clarifies which heatmap.2() arguments are reserved and which can be included in the coolmap call.
Bug fixes
Changes in version 1.10.0
BUG FIXES
Changes in version 0.99.7
Fix typo
Changes in version 0.99.6
Edit Vignette
Changes in version 0.99.5
Add PBMC dataset from ExperimentHub
Changes in version 0.99.4
Edit description
Changes in version 0.99.3
R>=3.6 generates a warning
Changes in version 0.99.2
change LRcell dependency to R>=3.6
Changes in version 0.99.1
change the .gitignore file
Changes in version 0.99.0
Changes in version 1.5.1
Update log from base 10 to base 2.
ZICP is now deprecated ()
SLM is removed in favor of a future R2 functionality for all models
Fitted values are returned along with residuals
Extracted random effects are also returned
Changes in version 2.8.0
NEW FUNCTIONS
ENHANCEMENTS
BUG FIXES
Changes in version 1.1.2
added feature-label output on May 10, 2021
added feature-label output on April 27, 2021
added cutoff value on March 06, 2021
Changes in version 1.1.1
hard-coding of alpha fixed on December 21, 2020.
Changes in version 1.2.1
Changes in version 0.99.12 (2021-05-18)
replace xlsx by openxlsx
Changes in version 0.99.11 (2021-05-10)
rename function normalize to normalizeAssay
rename function transform to transformAssay
rename function batch to batchCorrectionAssay
rename function impute to imputeAssay
Changes in version 0.99.10 (2021-05-06)
bump version to trigger building
Changes in version 0.99.9 (2021-04-29)
add hexbin in Suggests
fix bug in MAplot that plot is displayed properly
Changes in version 0.99.8 (2021-04-28)
set required version for S4Vectors to >= 0.29.15
Changes in version 0.99.7 (2021-04-28)
add version number of dependencies in Description file
Changes in version 0.99.6 (2021-04-27)
add MatrixQCvis to Watched Tags on the Bioconductor support site
Changes in version 0.99.5 (2021-04-27)
reduce file size of vignette by using partial_bundle for driftPlot
Changes in version 0.99.4 (2021-04-26)
add explained variance for PCoA
add se argument in create_boxplot that allows for ordering the samples
use ggplotly for driftPlot
allow flexible addition of samples in MA-plot based on a supplied character vector of sample names
return SummarizedExperiment when exiting the shiny application
add function maxQuant that allows for creation of SummarizedExperiment objects from maxQuant output (.xlsx files)
Changes in version 0.99.3 (2021-03-18)
reduce file size of vignette by using partial_bundle for plotly figures
Changes in version 0.99.2 (2021-03-18)
reduce resolution of images in vignette to reduce file size
Changes in version 0.99.1 (2021-03-17)
reduce file size of vignette
Changes in version 0.99.0 (2021-03-12)
write functions for data manipulation and plots
write tests for these functions
create UI and server modules for shinyQC
write tests for UI and server modules
load different UI elements depending on the type of data (if the data contains missing values or is complete)
Changes in version 1.17.1 (2020-11-27)
BUG FIXES
Changes in version 1.1.5
NEW FEATURES
Changes in version 0.99.11
Add support for STREME with runStreme(). STREME will supercede DREME in a future MEME Suite release.
Changes in version 0.99.10
Fixed a bug where paths weren’t correctly expanded when used as database entry under certain conditions
Changes in version 0.99.8
Removed inline r call in integrative_analysis vignette to fix issue on bioc build machine
Changes in version 0.99.7
Version bump to force pkg rebuild
Changes in version 0.99.6
updated ChIP-seq vignette to demonstrate this
Changes in version 0.99.5
renamed ame_plot_heatmap -> plot_ame_heatmap for consistency
Changes in version 0.1.2
runTomTom() dist default is now ed (changed from pearson).
Changes in version 0.1.0
Changes in version 1.1.3
Package additions
metabCombine(): main package workflow wrapper function
Parameter list functions for loading defaults of main workflow methods
Changes to labelRows
“conflict” argument replaced with “delta”, with default value (0.2)
default value of “minScore” argument increased to 0.5
Changes to calcScores
Changes to fit_loess
Changes to selectAnchors
default for “tolrtq” argument changed from 0.5 to 0.3
Changes in version 1.1.2 (2020-12-28)
Changes to fit_gam()/ fit_loess
new outlier detection method based on boxplot / IQR added
new argument: outlier, which accepts “MAD” or “boxplot” as a value
altered argument names: “frac” to “prop”, “ratio” to “coef”
documentation and minor code changes to main and supporting functions
Changes to plot_fit
new options for showing, hiding, or highlighting (with a legend) outliers
new arguments: outlier, which accepts “show” / “s”, “remove” / “r”, or “highlight” / “h” as arguments ; ocol, outlier point color if outlier argument set to “highlight” / “h”
Other changes
new test case for fit_gam()
Changes in version 1.1.1 (2020-12-02)
Bug Fixes
combinedTable check for missing group values (Issue #7)
calcScores / evaluateParams groups bug (Issue #8)
Warning for column names with bracket characters “{ ( [ ] ) }” (Issue #9)
QCol bug (Issue #10)
New Functionality
Changes in version 0.99
MetaboCoreUtils 0.99.1
MetaboCoreUtils 0.99.0
Changes in version 1.1.1
bug fixes
added some helper functions
Changes in version 1.7.2 (2020-12-17)
Changes in version 1.0.0
Changes in version 1.3.13 (2021-02-20)
NEW FEATURES
BUG FIXES
Changes in version 1.9.1
Changes in version 1.15.1
BUG FIXES AND IMPROVEMENTS
Changes in version 1.17.5
IMPROVEMENTS AND BUG FIXES
fread.gzipped: skip header rows in tabix file to fix
Changes in version 1.17.4
IMPROVEMENTS AND BUG FIXES
.setMethylDBNames: correct possible methylDBclass from “methylDB” to “methylRawDB”
fread.gzipped: disable skipping of decompression in fread.gzipped
can cause serious issues as investigated in and explained in
Changes in version 1.17.3
IMPROVEMENTS AND BUG FIXES
export methylRawListDB and methylRawList constructors
Changes in version 1.17.2
IMPROVEMENTS AND BUG FIXES
add faq section about merging methylRaw into methylRawList update vignette
Changes in version 1.17.1
IMPROVEMENTS AND BUG FIXES
readmethylDB: check if file exists before trying to read
Changes in version 1.9.5 (2021-05-04)
add functionality to adjust for multiple testing in correlation
return symmetric matrices when returning ppm ranges in structural
Changes in version 1.9.4 (2021-04-30)
add font in mz_vis to mono
split the example on how to use filter in mz_summary from the visualisation
Changes in version 1.9.3 (2021-04-28)
introduce AdjacencyMatrix S4 class, derived from SummarizedExperiment, to store the adjacency matrices. AdjacencyMatrix objects can be of type structural, statistical, and combine
adjust the documentation and tests for AdjacencyMatrix objects
add the functions mz_summary and mz_vis (contribution of Liesa Salzer)
Changes in version 1.9.2 (2021-03-24)
add section on structual matrix generation for directed=FALSE
Changes in version 1.9.1 (2021-02-20)
fix typos in the vignette
Changes in version 0.99.0 (2021-03-19)
Changes in version 0.99.0 (2021-03-19)
Changes in version 2.1.2 (2020-07-01)
Core heatmap labeling improved
aggregate_top_taxa deprecated
bimodality and potential_analysis functions fixed
Changes in version 2.1.1 (2020-04-06)
Added overlap function
Changes in version 1.0.3
added option to split a taxonomy column (as obtained via qiime) within the application
Changes in version 1.0.2
fixed bug in correlation analysis on phenotypes with NaN values
prevented application crash on loading ill-formatted feature data
Changes in version 1.0.1
adjusted to be compatible with shinyjs 2.0.0
Changes in version 1.3.11
fill ggclust bug to map color and shape. (2021-05-12, Wed)
Changes in version 1.3.9
more layouts for ggdiffclade. (2021-04-16, Fri)
Changes in version 1.3.8
add aliases for ggbartaxa and ggdiffbartaxa. (2021-03-23, Tue)
Changes in version 1.3.7
update import_qiime2 to avoid error when only feature table is provided. (2021-02-26, Fri)
Changes in version 1.3.6
convert svg dev to pdf dev. (2021-02-04, Thu)
Changes in version 1.3.5
fix an error for example of ggrarecurve. (2021-01-07, Thu) factorNames=”Group” to factorNames=”group”
Changes in version 1.3.4
geom_tiplab also support circular layout, so remove geom_tiplab2. (2020-11-26, Thu)
Changes in version 1.3.3
add as.treedata for taxonomyTable class. (2020-11-23, Mon)
Changes in version 1.3.2
rareres <- get_rarecurve(obj, chunks=400) p <- ggrarecurve(rareres)
Changes in version 1.3.1
Changes in version 0.99.15
fixes bug causing LRT to report wrong number of tested residues.
Changes in version 0.99.13
Changes in version 0.99.1 (2021-03-13)
Fix model normalisation bug - now using TMM normalisation by default. Log(M_s) offset can be used by passing norm.method=”logMS” to testNhoods.
Changes in version 0.99.0 (2021-03-04)
Submitted to Bioconductor
Changes in version 0.99.9 (2021-03-24)
Added new function, plotMetrics
mixtureModel now throws a warning if flexmix has not identified two distributions
Vignette includes instructions for assessing whether to use miQC on a dataset
Changes in version 0.1.0 (2021-02-10)
Submitted to Bioconductor
Changes in version 1.9.4-1.9.5
Add citation information <2021-04-15, Thus>
Changes in version 1.9.3
Add sponge module (SM) method <2021-02-02, Thue>
Changes in version 1.9.1-1.9.2
Update miRSM.R <2020-11-26, Thus>
Changes in version 1.17.1-1.17.2
Changes in version 0.99.11 (2021-05-14)
Changed News file
Changes in version 0.99.10
shrunk repo
Changes in version 0.99.9
updated with suggested notes
Changes in version 0.99.8
fixed check error
Changes in version 0.99.7
dealt with download issue
Changes in version 0.99.6
dealt with vignette issue
Changes in version 0.99.5
fixed documentation warnings for datasets and warnings for R CMD file size
Changes in version 0.99.4
fixed documentation warnings for datasets
Changes in version 0.99.3
fixed documentation warnings for code
Changes in version 0.99.2
initiated
Changes in version 0.99.11
Cleaner cache control.
Changes in version 0.99.9
Changes in the mistyR vignette to reflect changes to insilico evaluation from the paper.
Changes in version 0.99.0
Version with vignettes ready to submit to Bioconductor.
Changes in version 0.1.0
Changes in version 1.71.1
rda is defunct and all references are removed
bug in hclustWidget forbade use of more features than samples – this is fixed
Changes in version 1.39.1
use Imports rather than Depends
use Authors@R
KEGG.db (not available from BioC >= 3.13) -> KEGGREST
getGeneSets: only return descriptions for selected pathways
update example gene set
Changes in version 0.99.0 (2018-05-15)
Changes in version 1.1.9
integrated MEFISTO into MOFA2
Improve interoperability with Seurat and SingleCellExperiment
Improve memory usage and training time by optionally replacing float64 arrays with float32 arrays
mofapy2 has been updated to version 0.6.0 and now it has its own repository
Changes in version 1.1.4
integrated MEFISTO into MOFA2
Improving Python interface with basilisk
Sample metadata can be incorporated to the MOFA object before and after training
Changes in version 1.35.2
Changes in version 1.12.1
Fix argument checking in MPRASet construction to allow users to not have to specify barcode or eseq.
Fix bug with ordering of eids in log ratio object with aggregate=”none” option
Changes in version 0.99.4
Added the function PlotProteinPeptideRatio() to visualize a comparison between the proteins identified and the ratio Peptide/Proteins among Experiments.
Changes in version 0.99.3
Removed LazyData: TRUE.
Changes in version 0.99.2
Changes in version 1.24.0
release as part of Bioconductor 3.13
Changes in version 1.23.1
updated texshade.sty to newest version
Changes in version 1.23.0
new branch for Bioconductor 3.13 devel
Changes in version 0.99
Changes in 0.99.4
Changes in 0.99.3
Changes in 0.99.2
Changes in 0.99.1
Changes in 0.99.0
Changes in version 0.99
Changes in 0.99.3
Changes in 0.99.2
Changes in 0.99.1
Changes in version 1.3
Changes in 1.3.3
Changes in 1.3.2
Changes in 1.3.1
Changes in 1.3.0
Changes in version 2.17
Changes in 2.17.7
Changes in 2.17.6
Changes in 2.17.5
Changes in 2.17.4
Changes in 2.17.3
Changes in 2.17.2
Changes in 2.17.1
Changes in 2.17.0
Changes in version 1.1.1 (2020-03-27)
Changes in version 1.17.2
Update dev to match bug fixes in master
Changes in version 1.17.1
Update dev to match bug fixes in master
Changes in version 1.16.2
Author list updated
Changes in version 1.16.1
Update of createDatabase to record all intra average spectra in database
Add license and copyright info to code
Add github workflow CI (and subsequent formatting updates to pass tests)
Changes in version 0.99.6
Update authors in Description file
Changes in version 0.99.5
Fix standard errors on the model parameter estimates by msqrobLmer when using doQR = TRUE
Changes in version 0.99.4
Minor update vignette. Replace eval=FALSE in one R chunk so that the code is evaluated.
Changes in version 0.99.3
Avoiding sapply and 1:…
Changes in version 0.99.2
Changes in version 0.99.1
Changes in version 1.1.2
Updated Spectronaut converter to allow annotation in input file.
Changes in version 1.1.1
Changes in version 2.0.0 (2021-05-14)
Refactor the pacakge to make it modulized
Changes in version 1.8.2 (2020-12-17)
Update progress bar
Update groupComparisonTMT to avoid reusing the local function copied from lmer pacakge
Changes in version 1.8.1 (2020-12-10)
Add citation of the MSstatsTMT paper
Fix the bug in groupComparisonTMT() due to the update of dependent pacakge
Fix the bug in MedianPolish summarization
proteinSummarization(): replace the zero values with NA before and after peptide normalization
Changes in version 1.18.0
New features
Bug fixes and minor improvements
Changes in version 1.1.7 (2021-05-10)
Remove Biocarta database from vignette - it’s no longer supported by graphite R package.
List all available databases in error message.
Changes in version 1.1.5 (2021-04-19)
Typos fixed.
Add information and reference about metrics to calculate the feature ranks.
Changes in version 1.1.4 (2020-12-09)
Add the correct citation of the BMC Bioinformatics article.
Changes in version 1.1.3 (2020-11-19)
Prevent warning due to import of two different select() functions.
Changes in version 1.1.2 (2020-11-07)
Speed-up the metabolite ID mapping between different ID formats
Changes in version 1.1.1 (2020-11-05)
Bug fix. Prevent duplicated pathway title to cause an error.
Include new function to enumerate duplicted pathway titles with trailing numbers. 0.99.0
Changes in version 1.0.0
New Features
Changes in version 1.5.2
added edgeR::calcNormFactors() step in prepSim()
added argument ‘dd’ to simData() specifying whether or not to simulate 2 groups
prepSim() and simData() now support simulation of “singular” design (no samples, no clusters), as well as only samples/clusters
simData() defaults to simulating as many samples as available in order to avoid re-use (duplication) of reference samples
Changes in version 1.5.1
significant speed-up of aggregateData() by replacing usage of rowX() over a list with scuttle::summarizeAssayByGroup()
added options use “prop.detected” and “num.detected” as summary statistic (argument ‘fun’) in aggregateData()
added parallelization support in aggregateData() and pbDS() through argument BBPARAM (passed to scater::sumCountsAcrossCells() and BiocParallel::bplapply, respectively)
aggregateData() now stores the number of cells that went into aggregation under int_colData(.)$n_cells (vs. metadata(.)$n_cells) to support automated subsetting
replaced argument n_threads with BPPARAM throughout all parallelizable functions (aggregateData(), pbDS(), mmDS())
bug fix in prepSim(): the function previously failed when cluster/sample/group_id cell metadata columns were non-factors
bug fix in resDS(): cpm = TRUE previously didn’t handle missing cluster-sample combinations correctly
Changes in version 1.1.2 (2021-02-03)
RELEASE
Changes in version 3.1.4
Fixed spelling mistakes.
Changes in version 3.1.2
Plot_lesion_segregation has been improved. It can now plot multiple samples at the same time. Users can also specify which chromosomes they want to plot. The plot now also contains colour and the ratio of the mutations on the chromosomal strands is visualised by a horizontal line per chromosome.
Changes in version 3.1.2
Changes in version 2.25.5
Fix compile error on clang-11 reported (and fixed!) by Kurt Hornik, closes #244
Changes in version 2.25.4
Add dependency “rmarkdown” to “suggests:”
Changes in version 2.25.3
Ensure
header for CDF returns columns with correct data type.
Changes in version 2.25.2
Fix issue #238: ensure
header call returns the same columns for all
backends.
Changes in version 2.25.1
Bump version to trigger new build using latest Rcpp
Changes in version 2.25.0
New Bioc devel version
Changes in version 1.15.2
add rmarkdown as suggest package.
Changes in version 1.15.1
fix the missing link for rtracklayer::export.
Changes in version 1.1.4
Added plot_granges_heatmap() function to use GRanges for plotting heatmaps
Changes in version 1.1.3
Fixed error when reads overlap in name and position for internal function StatLM()
Changes in version 1.1.2
Added unit tests.
Changes in version 1.1.1
Changes in version 0.99.5 (2020-12-21)
Fix the issues from the build report
Changes in version 0.99.4 (2020-12-18)
Fix the issues from the build report
Changes in version 0.99.3 (2020-12-18)
Fix the issues from the build report
Changes in version 0.99.2 (2020-12-18)
Fix the issues from the build report
Changes in version 0.99.1 (2020-12-17)
Fix the issues from the build report
Changes in version 0.99.0 (2020-12-15)
Submitted to Bioconductor
Changes in version 1.1.1 (2021-05-04)
Changes in version 1.1.4
Changes
Changes in version 1.99.4 (2021-04-15)
Removal of MCUPGMA-dependencies for smaller networks.
Changes in version 1.99.0 (2021-03-08)
Fully rank based extension (netboost(…,robust_PCs=TRUE,filter_method=”spearman”,method=”spearman”)).
Full support of the non-parametric version.
Changes in version 1.7.3
Simplifed version of plotFastqcPCA. Now groups are an optional factor. No clustering is performed
Changes in version 1.7.2
Deprecated runFastQC
Changes in version 1.7.1
Added macs2 callpeak logs to importNgsLogs
Changes in version 1.6.1
Added asPercent to plotAlignmentSummary
Added the ability to assign new values via fqName<-
Changes in version 1.9.1
Changes in version 1.99.0
Included predNuPoP_chem function which predicts the nucleosome positioning based on profiles trained based on chemical maps
Vignette file has been created with R markdown
Added NEWS file to document version bump
Changes in version 2.7.1 (2020-11-11)
Changes in version 2.99.19
Fixed an error which resulted value 1 in the n_references columns even for records without references
Changes in version 2.99.17
Improved quality filtering of intercell networks
Changes in version 2.99.16
Quality filtering of intercell networks
Changes in version 2.99.13
More robust access to UniProt (in case of network failures)
Changes in version 2.99.11
Improved downloader backends
Changes in version 2.99.8
Database manager
Changes in version 2.99.7
Fixed many caching bugs
Changes in version 2.99.6
New resources: Human Phenotype Ontology and Gene Ontology annotations
Changes in version 2.99.0 (2021-03-08)
Changes in version 3.0
MAJOR change: frequency dependent fitness available.
Removed v.1 functionality.
Multiple initMutants.
Added MAGELLAN’s sources and functionality from MAGELLAN.
Changes in version 2.99.93 (2021-04-30)
Fixed bugs and improved testing of rfitness with three-element scale vector.
Changes in version 2.99.92 (2021-04-27)
rfitness: scale can take a three-element vector.
Vignette: examples (not run) for deviations from SSWM.
Changes in version 2.99.9 (2021-04-22)
Fixed date typo in one citation.
We were inconsistent, allowing some examples of one gene.
Readme: nem.
Changes in version 2.99.8 (2021-01-01)
Removing unused code.
Long tests: no longer using v.1.
Changes in version 2.99.7 (2020-12-30)
Vignette: fixed two missing refs and add seed in two examples.
Changes in version 2.99.6 (2020-12-30)
No longer v.1 functionality.
Slightly faster vignette.
Changes in version 2.99.5 (2020-12-18)
Random timeouts when building in tokay2 (Windows, BioC); fixing seed in vignette.
Changes in version 2.99.4 (2020-12-17)
Clean up of C++ code.
Changes in version 2.99.3 (2020-12-13)
Remove unnecessary (and cluttering) output and irrelevant warnings when running tests.
Decrease execution time of longer running examples in man (Rd) files.
Decrease time of vignette.
Changes in version 2.99.2 (2020-12-11)
Failed on test on Mac.
Changes in version 2.99.1 (2020-12-10)
Bump version number for BioC, so it will become version 3.0.0 in next release.
Latest version of exprtk.
Changes in version 2.21.995 (2020-12-09)
Vignette: rewrote most FDF examples using names (not numbers) for fitness specification.
Changes in version 2.21.994 (2020-12-08)
Can start simulation from arbitrary configuration: multiple init mutants (and multispecies functionality).
Freq-dep-fitness does not need to have a WT in fitness tables.
Bumped version (to 2.21.xyz) for new BioC devel.
Changes in version 2.0.0
MODIFICATIONS
added Rcpp code for online testing algorithms
added online batch algorithms of Zrnic et al. [2020]
added Storey-BH algorithm
added setBound function
updated vignette and pkgdown site
updated unit tests
updated references
Changes in version 3.11
Enhancements
Bug Fixes
Added a fix to the density estimate used by gate_tautstring
Changes in version 3.10
API Changes
Simple renaming
Classes and methods no longer exported
Bug Fixes
Changes in version 2.9.1
Changes in version 1.31.3
fix bug in mol.sum with single gene data reported by easygsea. Similarly add drop=F to a few other lines in mol.sum and node.map.
Changes in version 1.31.2
solve the check error due to the change related to KEGGEdgeSubtype in KEGGgraph package (version 1.51.1).
Changes in version 1.31.1
korg now include 6833 KEGG species or 1588 new species beyond 2017.
Changes in version 2.4.0
added DESeq2 section to vignette intro
permit that users can now specifiy just a single PC for plotloadings()
improved ellipse functionality with addition of parameters ellipseType, ellipseLevel, and ellipseSegments
over-rides ggrepel’s new default value for max.overlaps via introduction of maxoverlapsConnectors = 15
user can now specify a direction for connectors via directionConnectors
removed labhjust and labvjust
Changes in version 1.5.4 (2021-04-15)
mzML parameter parsing optimized
Changes in version 1.5.3 (2021-03-30)
Additional calculation of raw peak area without smoothing (peakArea Raw)
Alignment of peak integration algo across functions, integrateFIR() is now resilient to missing scans
Changes in version 1.5.2 (2021-01-31)
Change package alias due to overwritten .rd file warning on Windows (non case-sensitive name and path)
Move to Github Actions continuous integration
Changes in version 1.5.1 (2021-01-19)
Unittests updated to comply with new r-devel all.equal() environment checks behaviour
Changes in version 1.9.1 (2021-01-14)
CI TOOLS
BUG CORRECTION
Changes in version 0.99.12
Remove bugs in *.R, date: 2020.12.19.
Changes in version 0.99.11
We update the package after the first review.
Changes in version 0.99.7
Add pathway_info_hsa.rdata to data.
Changes in version 0.99.6
We update the package after the first review.
Changes in version 0.99.5
We update R version dependency from 4.0.0 to 4.1.
Changes in version 0.99.4
We subscribe to the bioc-devel mailing list
Changes in version 0.99.3
Remove bugs in *.R, date: 2020.11.19.
Changes in version 0.99.2
Remove bugs in *.R, date: 2020.11.8.
Changes in version 0.99.1
Remove bugs in *.R
Changes in version 0.99.0
Changes in version 0.99.0 (2021-02-17)
Changes in version 1.1.9
Fixes in documentation, examples and styles to meet BioC requirements
Changes in version 1.1.8
Fixes in documentation and examples to meet BioC requirements
Changes in version 1.1.7
Fixed getSPS to expect residue information.
Changes in version 1.1.6
Included warning signs to creating PhosphoExperiment object without attributes.
Changes in version 1.1.5
Fixed the warning message generated in plotQC for dendrograms. (Warning message: Vectorized input to element_text() is not officially supported.).
Changes in version 1.1.4
Fixed the parameter of plotQC from cols to grps
Changes in version 1.1.3
Changes in version 1.4.12
Changes in version 1.17.10 (2021-02-02)
Bug Fixes
Changes in version 0.99.4
Updated references
Changes in version 0.99.3
Accepted into bioconductor, will be released in next cycle
Changes in version 0.99.2
Lazydata set to false
Changes in version 0.99.0
Rewrote many data man pages
Changes in version 0.3.0
Changes in version 1.3.4
Added option to constrain spar values for QCRSC.
Changes in version 1.3.2
Added inputs/outputs for pqn.
Fixed glog plot bug.
Changes in version 1.2.1
Account for missing injections in QCRSC.
Changes in version 0.99.6 (2021-04-06)
Updated NEWS.Rd)
Changes in version 0.99.5 (2020-12-09)
Corrected name of an author)
Changes in version 0.99.4 (2020-12-09)
Changed R version dependency to >= 4.1 (R-devel)
Changes in version 0.99.3
Minor code changes as suggested by Bioconductor reviewer
Changes in version 0.99.2 (2020-11-11)
Changed arguments in examples to run faster
Changes in version 0.99.1 (2020-11-11)
Removed .Rproj file from repository
Changes in version 0.99.0 (2020-11-10)
Submitted to Bioconductor
Changes in version 1.24.0
release as part of Bioconductor 3.13
Changes in version 1.23.2
updates and documentation to vignette in order to adapt to newer version of Illumina’s TruSeq DNA Exome library prep kit
changed default col.names in readRegionsFromBedFile(); corresponding update of help page
Changes in version 1.23.1
re-created genome data objects (old data objects had become incompatible with newer ‘BSgenome’ version)
Changes in version 1.23.0
new branch for Bioconductor 3.13 devel.1.15
Bug fixed in PomaMultivariate
Changes in version 1.1.8
POMA 1.0.0
Changes in version 0.99
NEW FEATURES
Initial review.
Changes in version 0.99.0
Revise required files and format the code style.
Changes in version 1.1.22
Update package-down site
Update NEWS for Bioconductor 3.13
Changes in version 1.1.18
Gene expression data is now stored in the assays of the summarizedExperiment object returned by proActiv to facilitate easier filtering of the summarizedExperiment object. The metadata slot is now empty.
Plotting promoter activity: Implementation of boxplotPromoters function to plot boxplots of absolute promoter activity, relative promoter activity, and gene expression.
Identification of alternative promoters: Implementation of getAlternativePromoters, used to identify promoters that may exhibit alternative usage.
Changes in version 1.1.15
Implement getAlternativePromoters for identifying alternative promoters
Implement boxplotPromoters for visualizing promoter usage
Changes in version 1.1.6
Enforce condition vector to following naming conventions
Changes in version 1.31
Changes in version 1.31.3
Changes in version 1.31.2
Changes in version 1.31.1
Changes in version 1.31.0
Changes in version 1.23.9
Added new uniqueMsLevel generic <2021-04-08 Thu>
Changes in version 1.23.8
Added new filterPrecursorCharge generic <2021-04-06 Tue>
Changes in version 1.23.7
Add ProcessingStep object and related methods (moved from Spectra)
Changes in version 1.23.6
Added quantify generics (moved from MSnbase) <2021-01-02 Sat>
Changes in version 1.23.5
new alignRt generic.
Changes in version 1.23.4
new virtual Param class.
Changes in version 1.23.3
new filterIntensity generic.
Changes in version 1.23.2
new compounds generic.
Changes in version 1.23.1
new calculateFragments generic (moved from MSnbase)
Changes in version 1.18.0
Bug fixes and minor changes
Changes in version 0.99.5 (2021-04-08)
folder src-x64 and src-i386 in gitignore
Changes in version 0.99.4 (2021-04-08)
vignette: eval=FALSE in installation chuck
Changes in version 0.99.3 (2021-04-01)
added BugReports to description files
changed in vigette: remove echo = FASLSE and added installation section
remove dontrun from examples
avoided slot() and created generic method for slot access and setters
modyfied the two datSet documentaion
added documentation in inst/script
Changes in version 0.99.0 (2021-03-12)
Submitted to Bioconductor
Changes in version 1.22.0
NEW FEATURES
calculateNormalDatabase now suggests an off-target interval width that minimizes noise while keeping the resolution as high as possible
Added support for GATK4 CollectAllelicCounts output as alternative to Mutect
Added segmentationGATK4 to use GATK4’s segmentation function ModelSegments
SIGNIFICANT USER-VISIBLE CHANGES
Added min.total.counts filter to filterIntervals to remove intervals with low number of read counts in combined tumor and normal. Useful especially for off-target filtering in highly efficient assays where standard filters keep too many high variance regions.
Changed default of min.mappability in preprocessIntervals for on-target intervals to 0.6 (from 0.5)
Added min.mappability also to filterIntervals so that more conservative cutoffs can be tested after normalDB generation
PSCBS: 1.20.0 two-step segmentation slightly tweaked in that only high quality on-target intervals (high mappability and low PoN noise) are used in the first segmentation
Added –skipgcnorm flag to Coverage.R to skip GC-normalization
Added AF.info.field option to calculateMappingBiasGatk4 for non-standard GenomicsDB imports
If segmentation functions add breakpoints within baits, these breakpoints are now moved to the beginning or end of that bait to avoid that a single bait is assigned to two segments
Dx.R now always generates a _signatures.csv file with –signatures, even if insufficient number of mutations
Removed defunct calculateIntervalWeights function
BUGFIXES
Fix for nonsensical error message when VCF does not contain germline variants (#166).
Fix for various issues related to the seqlevelsStyle function (e.g. #171)
Fix for crash in calculateMappingBiasGatk4 when not all samples had a single variant call on a particular chromosome (chrY)
Fix related to annotating mapping bias with triallelic sites and GenomicsDB
Fixed an issue in Mutect 1.1.7 data in which good SNPs were ignored (#174)
Changes in version 1.29
qcmetrics 1.29.1
qcmetrics 1.29.0
Changes in version 1.1.0
QFeatures 1.1.4
QFeatures 1.1.3
QFeatures 1.1.2
Manually install preprocessCore (see for details) to use quantile normalisation in vignette and tests.
Update vignette to show normalize() and logTransform() directly on a QFeatures object and reference the QFeaturesWorkshop2020 workshop and WSBIM2122 chap 8.
QFeatures 1.1.1
QFeatures 1.1.0
Changes in version 1.9.4
Added documentation for new data set.
Changes in version 1.9.3
New Feature: Added the function IRSnorm, which performs normalisation of intensities across multiple TMT runs using a common reference sample (Internal Reference Scale).
Changes in version 1.9.2
Bug Fix: Update getContrastResults test reference
Fix bug in is_validScalingFunction - switch from
are_equal to
identical
Changes in version 1.9.1
Fix bug in getContrastRestults where file was written to
.txt, file
name
should now be correctly formed from the contrast name
Changes in version 0.99.0
All set for Bioconductor submission!
Changes in version 0.0.1
Added a NEWS.md file to track changes to the package.
Changes in version 1.0.1
Changes in version 1.16.0
New features
Changes in version 0.99.2 (2020-12-21)
code cleanup for bioconductor
initial submission to bioconductor
Changes in version 1.3.3 (2020-11-18)
Defunct function df_estimate()
Changes in version 1.2.1 (2020-11-17)
pFdr adapted according to (Phipson and Smyth 2010)
Changes in version 1.31.1
NEW FEATURES
Changes in version 1.11
Changes in version 1.7.12 (2021-02-24)
Use Basilisk to manage python dependencies (cwltool).
Rename of ‘cwlParam’ into ‘cwlProcess’, ‘cwlStepParam’ into ‘cwlWorkflow’.
Add the support of wrapping R functions into Rcwl tools.
Changes in version 1.7.7 (2021-02-24)
Moved all recipes to.
Added new core functions: cwlUpdate, cwlSearch and cwlLoad.
Core functions return a ‘cwlHub’ object.
Changes in version 2.12.0
Consistent interchangeable handling of node|edge|network names and SUIDs
createNetworkFromDataframes plays nice with tibbles
Changes in version 1.0
Changes in version 0.0.0.9000
Changes in version 1.5.2 (2021-04-16)
Added check to ensure that clustering was performed in Seurat objects prior to the pathway analysis.
Changes in version 1.5.1 (2021-04-01)
Fixed bug in perform_reactome_analysis: Error messages were not displayed correctly.
Changes in version 1.2.0
Added the rmd2id() function to easily determine the ID for each chapter.
Link to the originating chapter for the set-up code in extractCached().
Expose collapseStart() and collapseEnd() for manual creation of collapsible chunks.
Added scrapeReferences() to scrape a bookdown book for references for external use.
Added configureBook() to configure a Bioconductor package as a book deployment.
Added link() to rapidly link to references in a configured Bioconductor book package.
Added extractFromPackage() to extract objects from Rmarkdown files in installed packages.
Added createRedirects() to redirect from old, deprecated pages to their new locations.
Changes in version 1.1.7
BUG FIXES
read_counts() now reads the gene/exon counts for every sample as numeric instead of integer in order to support count values that exceed the 32bit integer threshold (such as 2447935369). Previously, read_counts() would report tiny fractions for such large numbers. This bug was reported by Christopher Wilks.
Changes in version 1.1.6
BUG FIXES
Now project_homes() reads in a text file from recount3_url/organism/homes_index which enables support for custom URLs such as.
Changes in version 1.1.4
BUG FIXES
Fixed project_homes(), available_projects() and available_samples() to support using non-standard recount3_urls where the user knows that are the project_homes() for their organism of choice. This fix enables users to create their own custom recount3-like webservers and access their data using the functions in this package. This fix introduces the argument available_homes to both available_projects() and available_samples(). This bug was reported by Christopher Wilks.
Changes in version 1.1.3
NEW FEATURES
Added expand_sra_attributes() that was contributed by Andrew E Jaffe. This function expands the SRA attributes stored in a given SRA study, which makes it easier to use that data. However, it makes it harder to merge studies and thus should be used with caution.
Changes in version 1.1.1
BUG FIXES
Changes in version 1.1.4
Improves User’s Guide, fixes typos, new citation, adds disclaimer text, updates servermatrix() chunk.
Updates examples to further limit downloads. Function get_rmdl() uses download = FALSE,
Updates Data Analyses vignette. Uses reduced dpi for images in Data Analyses vignette to limit package size. Uses updated metadata file name.
Compresses new metadata v.0.0.2 files to limit package size.
Uses uniform metadata file label for v.0.0.1 file.
Changes in version 1.1.3
Added v.0.0.2 database compilation files to server (recount.bio/data) and revised recountmethylation functions for cross-platform support. The new files reflect IDAT downloads completed in Nov 2020 from GEO/GDS, including the first compilations of EPIC/HM850K arrays.
Added
platform argument in relevant
getdb functions.
Added
which.platform argument to
get_rmdl
Added new function
smfilt to filter server data table for
newest compilation files, accounting for platform in the
filename.
Cleaned up and shoretened the
servermatrix function. This now
handles RCurl call for “dn” (originally from
get_rmdl) when
handling condition
dn = NULL.
Updated the User’s Guide to fix typos, reflect v.0.0.2 samples, and add a download troubleshoot section. Added numeric citations format, removed evaluation of validation section due to possible package build failure from bad internet connection.
Updated ExperimentHub file metadata script and table to add new v.0.0.2 compilation files.
Renamed sample metadata directory to “gsm_metadata” to avoid confusion with “metadata.csv” file table for hubs.
Changes in version 1.3.2
SIGNIFICANT USER-VISIBLE CHANGES
The link provided inside connect_database() has been updated in order to connect with the latest version of regulonDB v10.8.
Changes in version 1.3.1
BUG FIXES
Changes in version 1.11.1
NEW FEATURES
SIGNIFICANT USER-VISIBLE CHANGES
removed is_GMQL from read_gmql function
The entire dataset must have the right folder structure in order to
works correctly
Swap order of arguments ‘dir_out’ and ‘name’ of the collect() function so now the latter comes before the former.
DEPRECATED AND DEFUNCT
BUG FIXES
Changes in version 2.36.0
NEW FEATURES
Added additional hyberslab selection functions introduced in HDF5 1.10.7 (H5Scombine_hyperslab, H5Scombine_select, H5Sget_select_npoints).
Support for read access to files in S3 buckets now includes Windows.
Added function h5deleteAttribute().
BUG FIXES
Changes in version 1.4.0
USER VISIBLE CHANGES
Compression libraries updated:
zstd: 1.3.8 🠪 1.4.5
BUG FIXES
Changes in version 1.14
New features
Bug fixes
CPPFLAGS used to build R are now used during HDF compilation.
Package configure script will now stop if it encounters errors when compiling HDF5. This should make diagnosing issues easier.
Changes in version 0.99.3
Renamed R functions by following bioconductor convention
Changes in version 0.99.2
Initial version for review
Changes in version 1.3.4
add rmarkdown as suggest package.
Changes in version 1.3.3
add github action.
Changes in version 1.3.2
fix the issue if there is softclip in the mapping reads and the reads length is smaller than shfit range.
Changes in version 1.3.1
keep the raw counts for countReads.
Changes in version 0.99.0 (2020-10-21)
Changes in version 1.7.1
Changes in version 1.5.4 (2021-01-23)
add plot type “points” to plotCompare functions
Changes in version 1.5.3 (2021-01-12)
bugfix for zero-length annotation
bugfix for settings function
bugfix for plotting functions
Changes in version 1.5.2 (2020-12-12)
bugfix for names plotted by plotCompareByCoord
Changes in version 1.5.1 (2021-01-12)
Changes in version 1.5.1 (2021-01-12)
Changes in version 2.9.3
Changed some of the default options values
Some bugfixes
Changes in version 2.9.2
Implemented function rnb.execute.pOOBAH. Thanks to Nathan Steenbuck.
Update of contact information in DESCRIPTION
Changes in version 2.9.1
Improved function intensities.by.color. Thanks to Nathan Steenbuck.
Changes in version 2.19
CHANGES IN VERSION 2.19.4
CHANGES IN VERSION 2.19.3
CHANGES IN VERSION 2.19.2
CHANGES IN VERSION 2.19.1
Changes in version 1.23.12
MINOR MODIFICATION
minor documentation update
Changes in version 1.23.8
MINOR MODIFICATION
vignette: minor update
Changes in version 1.23.6
MINOR MODIFICATION
‘view’ method: minor update of documentation
Changes in version 1.23.4
BUG FIXED
‘view’ method: display of row names
Changes in version 1.23.2
BUG FIXED
Changes in version 1.99.01
Changes in version 1.99.0
rpx 1.99.8
rpx 1.99.7
rpx 1.99.6
rpx 1.99.5
rpx 1.99.4
rpx 1.99.3
rpx 1.99.2
rpx 1.99.1
Changes in version 1.27.0
Changes in version 1.3.1
Changes in version 2.8
NEW FEATURES
Changes in version 2.6.0
Improved the speed of cellCounts and also reduced its memory use.
Added a parameter ‘umi.cutoff’ to cellCounts to call all the cells that had a total UMI count greater than the specified threshold.
Added support for FASTQ-format read input in CellCounts.
Changes in version 1.3.2 (2020-11-24)
Changes in version 2.22.0
New features
Bug fixes and minor improvements
Changes in version 2.16.0
Changes in version 1.16.0
Changes in version 1.16.0
Changes in version 1.1.2 (2020-11-27)
Changes in version 1.12.0
Removed getColoredPathway
New function: writeGMT
Updated URLs to BridgeDb datasources.tsv (again)
Bug fix: downloadPathwaysArchive works with redirected urls
Changes in version 1.11.4
Updated URLs to BridgeDb datasources.tsv
Changes in version 1.11.3
New features
Changes in version 0.30.0
NEW FEATURES
Add combineRows(), combineCols(), and combineUniqueCols() for DataFrame objects. These are more flexible versions of rbind() and cbind() that don’t require the objects to combine to have the same columns or rows.
Add unname() generic and a method for Vector objects.
DEPRECATED AND DEFUNCT
BUG FIXES
Fix long-standing bug in rbind() method for DataFrame objects. The bug was causing rbind() to return an incorrect result when the columns of the DataFrame objects to combine were a mix of ordinary lists and other list-like objects like IntegerList objects (defined in the IRanges package).
Fix issues in DataFrame printing (commits 735c6b7f and 89b045e7).
Fix bug in expand() when the DataFrame object to expand has one or none unselected columns (commit a8f839bb).
Changes in version 1.6.0
seqFitNullGLMM_SPA() can use imputed dosages directly without
converting the dosages to the best-guess genotypes
new function
glmmHeritability() for approximate heritability
estimates
Changes in version 1.16.0
BUG FIXES
Changes in version 0.99.0 (2021-01-06)
Changes in version 0.99.0
NEW FEATURES
SIGNIFICANT USER-VISIBLE CHANGES
BUG FIXES
Changes in version 1.5.1
Changes in version 1.5.60 (2021-05-18)
Changes in version 1.0.0
Changes in version 1.20.0
runMDS can use user-supplied function for calculating the distance matrix. runMDS can optionally store the distance matrix computed. runMDS also stores the eig and GOF fields of the object returned.
Made the handling of center, scale, color and limits similar in plotDots, plotHeatmap, and plotGroupedHeatmap
Add use_fitsne argument to runTSNE allowing the use of fast interpolated t-SNE in place of Barnes-Hut t-SNE.
Changes in version 0.99.5 (2020-12-30)
Changes in version 1.5.11 (2021-01-19)
scDblFinder now provides doublet enrichment tests
doublet generation and default parameters have been further optimized
Changes in version 1.15.1 (2021-05-06)
Add PsiNorm normalization method and its wrapper.
Add vignette that describes how to use PsiNorm.
Changes in version 1.1
scp 1.1.6
scp 1.1.5
scp 1.1.4
scp 1.1.3
scp 1.1.2
scp 1.1.1
scp 1.1.0
Changes in version 1.5.3 (2021-03-14)
Moving ScaledMatrix to “imports” section of DESCRIPTION.
Changes in version 1.5.2 (2020-12-21)
Adding LTLA/ScaledMatrix to “Remotes” section of DESCRIPTION.
Changes in version 1.5.1 (2020-12-17)
Changes in version 1.20.0
All deprecated functions from the previous release are now defunct.
Added a simplify= option to quickSubCluster() to get the cluster assignments directly.
Deprecated combinePValues() as this is replaced by metapod::combineParallelPValues().
getClusteredPCs() now uses bluster::clusterRows() by default.
decideTestsPerLabel() now automatically detects pval.field= if not supplied.
Added the clusterCells() wrapper around bluster functionality.
Removed the option to pass a matrix in design= from pseudoBulkDGE().
Migrated all normalization-related functions (computeSumFactors(), calculateSumFactors(), cleanSizeFactors() and computeSpikeFactors()) to a better home in scuttle. Soft-deprecated existing functions.
Modified getTopHVGs() to accept a SingleCellExperiment and compute the DataFrame with modelGeneVar().
Added fixedPCA() to compute a PCA with a fixed number of components, a la scater::runPCA() (but without requiring scater).
Modified denoisePCA() so that it now complains if subset.row= is not provided.
Modified all pairwise* functions so that the p-value from direction=”any” is derived from the two p-values from the one-sided tests. This is necessary for correctness with all choices of lfc= and block=, at the cost of conservativeness when block=NULL and lfc is large.
Changes in version 1.2.3
Changed the access of the sample data to github.io repo: readRDS(url(“”))
Changes in version 1.2.2
Removed Startrac-based functions in order to pass build on Bioconductor. DEPRECATED AND DEFUNCT
Deprecate StartracDiversity()
Changes in version 1.2.0
SUBMITTED
SIGNIFICANT USER-VISIBLE CHANGES
DEPRECATED AND DEFUNCT
Deprecate combineSeurat in favor or combineExpression().
Deprecate seurat2List in favor of expression2List().
Changes in version 1.1.2
Clonal Overlap Coefficient issue fixed, was comparing unique barcodes and not clonotypes
Added function checkBlanks to remove list elements without clonotypes, this prevents errors for visualizations
Re-added Startrac metrics by stripping down the package and adding it piecemeal
Heavily modified dependencies to reduce total number
Changes in version 1.2.0
Migrated whichNonZero() to beachmat.
Bugfixes for factor-based colData aggregation in aggregateAcrossCells(). Added proper support for Vectors.
Bugfix for correct response to use.altexps= in perCellQCMetrics(), perFeatureQCMetrics().
Added a normalize.all= option to normalizeCounts(). Removed unnecessary warning when down.target= is not specified. Exposed the default size.factors= in the SingleCellExperiment method.
Modified the SingleCellExperiment method of logNormCounts() so that manually specified size factors do not apply to alternative Experiments. Only relevant if size.factors= and use.altexps= are specified.
Deprecated use.altexps= in favor of applySCE() in logNormCounts() and aggregateAcrossCells().
Renamed addPerCellQC() and addPerFeatureQC() to addPerCellQCMetrics() and addPerCellFeatureMetrics(), for consistency. Soft-deprecated the old functions.
Moved most of quickPerCellQC() functionality into the new perCellQCFilters() function. Repurposed the former to directly return a filtered SummarizedExperiment object.
Migrated scran’s normalization-related functions into this package. Added pooledSizeFactors(), computePooledFactors(), cleanSizeFactors() and computeSpikeFactors().
Added transform=”asinh” to normalizeCounts() and logNormCounts() for inverse hyperbolic transformations of CITE-seq data.
Modified isOutlier() to now return outlier.filter objects. These are simply logical vectors that preseve the “thresholds” attribute upon subsetting.
Migrated correctGroupSummary() from scater, to compute corrected versions of group-level summary statistics.
Changes in version 1.11.5
return beta and gamma as matrix
Changes in version 1.11.4
update vignette with SC RNA sequencing data
Changes in version 1.11.2
re-upload files under Version 1.11.1
Changes in version 1.11.1
update reference manual with single-cell RNA sequencing data
Changes in version 1.0.0 (2021-04-19)
sechm moved from the SEtools package
generalized annotations
Changes in version 1.23.1
Upgraded datasets to hg38 and mm10
Upgraded python script from python2 to python3
Changes in version 1.32.0
NEW FEATURES
new option ‘ret.idx’ in
seqSetFilter() for unsorted sample and
variant
indices
new option ‘ret.idx’ in
seqSetFilterAnnotID() for unsorted variant
index
rewrite the function
seqSetFilterPos(): new options ‘ref’ and
‘alt’,
‘multi.pos=TRUE’ by default
new option ‘packed.idx’ in
seqAddValue() for packing an indexing
variable
new option ‘warn’ in
seqSetFilter() to enable or disable the
warning
new functions
seqNewVarData() and
seqListVarData() for
variable-length data
UTILITIES
allow no variant in
seqApply() and
seqBlockApply()
the list object returned from
seqGetData() always have names if
there
are more than one input variable names
BUG FIXES
seqGDS2VCF() should output “.” instead of NA in the FILTER column
seqGetData() should support factor when ‘.padNA=TRUE’ or
‘.tolist=TRUE’
fix
seqGDS2VCF() with factor variables
seqSummary(gds, "$filter") should return a data frame with zero row
if
‘annotation/filter’ is not a factor
Changes in version 1.1.1 (2021-01-22)
Changes in version 1.31.1 (2020-11-30)
Changes in version 1.5.3 (2021-04-19)
Changes in version 1.5.0
shareAttributesand
minLengthin package options
depthin function is.shared
Changes in version 0.99.9 (2021-01-07)
Bug fixed: DMR plot group colors
Changes in version 0.99.0 (2020-11-13)
Submitted to Bioconductor
Changes in version 1.50
NEW FEATURES
(v 1.49.1)
as(., "QualityScaledDNAStringSet") propagates
names. See.
(v 1.49.1) implement
as(., "DNAStringSet"). See.
BUG FIXES
Changes in version 1.5.3 (2021-04-12)
Supported setReadable function and readable argument in TSEA functions to convert Entrez id to gene Symbols in the itemID column in the enrichment result table.
Supported dtnetplot on Reactome pathway
Changes in version 1.5.2 (2021-02-22)
Changes in version 1.3.1 (2020-11-11)
Speed up
Modified more defaults based on publicaly available FFPE samples
Added new parameter sameChrProp for a better simulation
Modified the model of SRCR distance for adjcent ss-DNA combination: from normal distribution to log-normal distribution
Renaming of parameters
Fixed the bug of producing chimeric reads without SRCR
Fixed the bug of producing read duplicates at low coverage
Changes in version 1.1.4
add
export_to_shiny_app()
add
simplifyGOFromMultipleLists()
Changes in version 1.1.2
add
anno_word_cloud() function
Changes in version 1.14.0
Added the unsplitAltExps() function to reverse the effect of splitting alternative experiments.
Added a mainExpName() getter and setter to remember the name of the main experiment.
splitAltExps() will now store the chosen ref as the mainExpName.
swapAltExp() now discards the promoted experiment from the list of alternative experiments in the output. It will also exchange the colData between the swapped experiments when withColData=TRUE. These changes assist in achieving reversibility of the output.
Added applySCE() to conveniently apply a function to the main and alternative Experiments.
Added withDimnames= to reducedDim<-() and reducedDims<-(). If TRUE, these methods now emit warnings on observing incompatible row names in value.
Respect any metadata passed in with value in reducedDims<-() and altExps<-().
Added the reduced.dim.matrix class to preserve attributes inside the reducedDims during subsetting/combining.
Setting withColData=TRUE in altExp() and altExps() will now prepend colData(x) to the output colData.
Added withDimnames= to altExp<-() and altExps<-(). If TRUE, these methods now emit warnings on observing incompatible column names in value. Also added withColData=, which will now reverse the prepending in the getter if the left-most columns are the same as colData(x). (If not the same, a warning is emitted.)
Changes in version 2.1.2 (2021-05-13)
Added diffAbundanceFET and plotClusterAbundance function
Linked Shiny UI help buttons to new online help pages
Expanded convertSCEtoSeurat() function to copy additional data
Updated and merged pkgdown documentation
Added HTML reports for Seurat curated workflow and marker finding
Refactor of Normalization UI
Added tagging system for matrix type
Several bug fixes
Added generic wrapper functions for normalization, dimensionality reduction and feature selection
Changes in version 2.0.1 (2021-01-07)
Added cell type labeling functional, wrapping SingleR method
Added cell type labeling UI under differential expression tab
Added marker identification in Seurat workflow
Changes in version 1.6.0
Relaxed the requirements for consistent row names in combineRecomputedResults().
Support sparse DelayedArray inputs in classifySingleR().
Parallelize over labels instead of rows in aggregateReference(), with minor changes in the setting of the seed. Restrict the PCA to the top 1000 most highly variable genes, for speed.
Changes in version 0.0.1 (2021-02-07)
NEW FEATURES
Changes in version 1.7.8
Change default ‘minSNP’ value for ‘parallelSites’ function.
Changes in version 1.7.7
Fix: Add ‘rmarkdown’ in ‘Suggests’.
Only plot paths with duplication in number for ‘sneakPeek’ function.
Changes in version 1.7.6
Bug fix: empty groups produced by ‘groupTips’ function.
Create ‘paraFixSites’ and ‘fixationIndel’ functions.
Changes in version 1.7.5
Treat ‘phyMSAmatched’ object as ‘lineagePath’ class for simplicity.
Improved multiprocessing.
Fix: repeated cluster name by ‘.assignClusterNames’ internal function.
Rename ‘allSitesPos’ to ‘allSitesName’.
Add ‘plotMutSites’ support for ‘lineagePath’ and ‘fixationSites’ objects.
Changes in version 1.7.4
‘cl.cores’ option for turning multiprocessing on and off.
Changes in version 1.7.3
Fix: inability to get position of all the sites.
Changes in version 1.7.2
Fix: missing export for ‘plot.phyMSAmatched’ function.
Fix: ‘addMSA’ function unable to handle ‘treedata’ object.
Multiprocess for ‘addMSA’ and ‘sitesMinEntropy’ function.
Changes in version 1.7.1
Guess sequence type based on ATCG proportion for ‘addMSA’.
Changes in version 2.0.0
Added a NEWS.md file to track changes to the package.
Changed default output of most functions from SlingshotDataSet to PseudotimeOrdering and added conversion functions between them and SingleCellExperiment.
getLineages now relies on createClusterMST
Removed plotGenePseudotime
added as.df option to slingCurves and slingMST, which provide relevant information for plotting as data.frame objects. This should help those plotting Slingshot results with ggplot, especially for our traffic package.
updated all documentation.
Changes in version 1.5.0
New Features
Bug Fixes
Changes in version 1.1.700 (2021-05-05)
updating roles in DESCRIPTION file
adding GeneExpression biocVie
switching LazyData to false
fixing return value in show method documentation
Changes in version 1.1.434 (2021-26-02)
fixing subset method according to SummarizedExperiment generic definition
Changes in version 1.1.432 (2021-15-02)
fixing documentation on latex errors
Changes in version 1.1.430-1.1.431 (2021-12-02)
adding BumpyMatrix as suggests
update documentation
Changes in version 1.1.429 (2021-12-02)
adding cd_keep = TRUE binds all the colData to the spatialData
fixing bug for cd_keep with multiple elements
Changes in version 1.1.428 (2021-12-02)
adding itemize to assays vignette item
correcting typo cd_keep->cd_bind in spatialData documentation
Changes in version 1.1.427 (2021-09-02)
fixing tenx vignette
Changes in version 1.1.426 (2021-09-02)
fixing read10xVisium example with data parameter
Changes in version 1.1.425 (2021-08-02)
restoring data parameter in read10xVisium
missing itemize in combine documentation
Changes in version 1.1.424 (2021-07-02)
cleaning documentation
removing spatialImage-methods.R file
Changes in version 1.1.423 (2021-02-02)
fixing documentation issues on imgData
Changes in version 1.1.422 (2021-29-01)
removing ve data because of local image problem (using example(read10xVisium) instead)
Changes in version 1.1.421 (2021-28-01)
fixing ve data local image problem
Changes in version 1.1.42 (2021-21-01)
implementing new SpatialExperiment class
spatialData slot
imgData and image handling methods (HLC)
Changes in version 1.1.6 (2021-02-04)
removed additional slots in the SPE class definition (i.e. spatialData and spatialCoordsNames)
spatialCoords stored in int_colData() = numeric matrix
spatialDataNames stored in int_metadata() = character vector specifying a subset of colData()
the SPE show method does not include spatialData in colData; instead, spatialData/CoordNames are printed separately
the SPE constructor now allows specification of spatialData/Coords/-Names where -Names can be a subset of the supplied colData(); spatialData/Coords are thus optional
cbind() now allows duplicated sample_ids, which are made unique with a message
consistent usage of “spe” for SpatialExperiment objects across all examples (previously, both ve and se were used as well)
fixed cache/path-related error on windows in SpatialImage unit tests
added unit-tests of SpatialExperiment class validity
imgData field in int_metadata is now required to exist (but can be an empty DFrame)
colData<- protects sample_id & spatialDataNames fields; spatialData<- protects colData
Changes in version 1.1.5 (2021-31-03)
version bump to x.y.z format with .z increment
general code-style revision to keep to Bioc guidelines including, e.g.
usage of accessors (and not @)
keeping to a 80-character limit
spaces around logical operators (but not function arguments)
in-line { for function definitions, if-else statements etc.
re-ordering of roxygen2 documentation to be consistent across scripts
Changes in version 1.1.6 (2021-05-17)
The spatial heatmaps are able to maitain outline (stroke) widths defined in aSVG. The stroke widths can be updated with “update_feature”.
Text in aSVGs can be independent from features, i.e. have separate colors, stroke widths, etc.
Only “g”, “path”, “rect”, “ellipse”, “use”, and “title” elements are allowed in aSVG files, and other elements will raise errors or warnings. The “use” element should not in “g”, and “g” elements should not have the “transform” attribute with a “matrix” value.
Extraction of shape coordinates includes two alternative methods. If one fails, the other will be used by default. So in most cases though some coordinates are missing due to irregular shapes, spatial heatmaps can still be created.
Added spatiotemporal example of rice coleoptile to Shiny app and vignette.
Downloaded gene expression data are cached.
In “spatial_hm”, the “tis.trans” argument was replaced by “ft.trans”; width and height arguments were removed, since the spatial heatmap aspect ratio is set the same with original aSVG.
Shiny app: the function “shiny_all” was renamed to “shiny_shm”; the app is able to take HDF5 database backend, which contains data and aSVG files, and the HDF5 database can also be uploaded on the user interface; re-organized user interface: Landing Page (includes links to different app instances), Spatial Heatmap (includes sub-tabs of Image, Interactive, Video, Matrix Heatmap, Interactive Network), Spatial Enrichment (identifies spatial feature-specific genes), About; new functionality introduced: auto-completion search box, URLs of specific app states can be bookmarked, full screen, scrolling height, tooltip, one-to-multiple re-matching of spatial features, fixed aspect ratio (SHMs are not squeezed in the case of multiple aSVGs), metadata column and link column in the data matrix; code was organized in modules, etc.
Changes in version 1.1
Changes in 1.1.20
Changes in 1.1.19
Changes in 1.1.18
Changes in 1.1.17
Changes in 1.1.16
Changes in 1.1.15
Changes in 1.1.14
Changes in 1.1.13
Changes in 1.1.12
Changes in 1.1.11
Changes in 1.1.10
Changes in 1.1.9
Changes in 1.1.8
Changes in 1.1.7
Changes in 1.1.6
Changes in 1.1.5
Changes in 1.1.4
Changes in 1.1.3
Changes in 1.1.2
Changes in 1.1.1
Changes in 1.1.0
Changes in version 1.7.1 (2020-11-22)
Changes in version 1.16.0 (2020-05-20)
• Added ability to simulate data with complex multiplexed sequencing designs
• Added simulation of “conditional” effects, where a subset of DE and eQTL effects are applied to only a subset of individuals (e.g. disease vs. healthy samples)
• Added the ability to simulate different numbers of cells for each sample, sampled from a gamma distribution.
• Updates to the splatPop vignette describing these changes
Logical matrices should now be handled correctly when minimising output SingleCellExperiment objects
Other minor fixes
Changes in version 0.99.18
R version update
Changes in version 0.99.17
Minor corrections
Changes in version 0.99.16
Minor corrections
Changes in version 0.99.15
Adjust sample dataset creating script to the use of SummarizedExperiment
Changes in version 0.99.14
Documentation updates
Changes in version 0.99.13
Documentation and example updates
Changes in version 0.99.12
Documentation and example updates
Changes in version 0.99.11
Vignette updates
Changes in version 0.99.10
Example dataset updates
Changes in version 0.99.9
Documentation and code formatting updates.
Changes in version 0.99.8
Examples for diversity calculation functions.
Changes in version 0.99.7
Formatting corrections.
Changes in version 0.99.5
Added verbose argument for functions.
Changes in version 0.99.4
Updates to example dataset.
Changes in version 0.99.3
SummarizedExperiment input type updated in calculate_diversity, new argument: SE_assay.
Documentation, vignette updated.
Changes in version 0.99.2
SummarizedExperiment input type instead of ExpressionSet.
Changes in version 0.99.1
Correction: unnecessary file removed.
Changes in version 0.99.0
Changes in version 1.21.1
Changes in version 1.4.0
added VIP summary chart
add ellipse plotting options to pca_scores_plot
mv_sample_filter can be used in train/predict mode
Documentation updates
Minor issue fixes
Add median method for fold change
Update PQN with new inputs/outputs due to changes in pmp package
Update SBC with new inputs/outputs due to changes in pmp package
Update MTBLS79 due to changes in SBC
Changes in version 1.22.0
NEW FEATURES
Changes in version 0.99.9 (2021-02-19)
Fixed NEWS text formatting
Changes in version 0.99.8 (2021-02-11)
Fixed multiple issues in review for development
No longer using for loops in function code
Changes in version 0.99.0
Changes in version 1.21.2
BUG FIXES
add rmarkdown to DESCRIPTION
Changes in version 1.21.1
UPDATE
update axis.text and theme_bw
Changes in version 1.21.0
NEW FEATURES
Changes in version 1.3.15
Changes to concensus score in PairSummaries.
Changes in version 1.3.14
Major changes to the PairSummaries function and minor changes to NucleotideOverlaps, ExtractBy, and FindSets. Adjustments to the model that PairSummaries calls on to predict PIDs.
Changes in version 1.3.13
DisjointSet function added to extract single linkage clusters from a PairSummaries object.
Changes in version 1.3.12
PairSummaries now computes 4-mer distance between predicted pairs.
Changes in version 1.3.11
The function FindSets has been added and performs single linkage clustering on a pairs list as represented by vectors of integers using the Union-Find algorithm. Long term this function will have a larger wrapper function for user ease of access but will remain exposed.
Changes in version 1.3.10
NucleotideOverlap now passes it’s GeneCalls object forward, allowing PairSummaries to forego inclusion of that object as an argument.
Changes in version 1.3.9
Minor vignette and suggested package changes.
Changes in version 1.3.8
PairSummaries now allows users to fill in specific matching gaps in blocks of predicted pairs with the arguments AllowGaps and OffSetsAllowed.
Changes in version 1.3.7
PID prediction models in PairSummaries adjusted.
Changes in version 1.3.6
Contig name matching has been implemented. Scheme expects users to follow NCBI contig naming and gff formats, accepting contig names from gffs directly, and removing the first whitespace and everything thereafter from FASTA headers. Contig name matching can be disabled if users wish, using the argument AcceptContigNames, but ensuring that the correct contigs in GeneCalls objects are matched to the appropriate contigs in Synteny objects are then the user’s responsibility.
Changes in version 1.3.5
gffToDataFrame now parses out the transl_table attribute
Changes in version 1.3.2
Changes in version 1.1.40
Major change
Add is_demo option: only affect workflow module right now. Lock users inside a temp folder when using the WF module and give users a new temp folder every time they refresh. This will prevent directory exist problem if many users are using a same deploy instance.
Add welcome_guide option: whether to enable the welcome guide which highlights the guide dropdown menu.
Rewrite welcome tab with a gallery to show all SPS features.
loadDF, dynamicFile and dynamicFileServer added back to this mainframe work package instead of spsComps, because these dependencies have already been using in SPS. Leave these functions in spsComps will introduce extra dependencies, and these functions are not too frequently used outside the framework.
Minor change
Option warning_toast now also checks if you are on “local” mode.
Deleted some unwanted entries in reference generating yaml file.
Fix some typos.
More informative error message when the config file cannot be found for spsOptions
Add some .onLoad methods so users can use the spsOption to get default values on package load.
Updated essquise functions
Add more guides.
Removed the scroll to top button by shinyDashboardPlus, we have our own “go top” button.
Add assertions to spsInit.
Add some screenshots to readme.
Bug fix
Fix a warning in vroom due to the column type problem
Changes in version 1.1.35
Major change
Login feature added:
Users can choose whether to enable the login or not in global.RSPS options.
There are also the login loading screen feature which can be turned on and off.
There are 3 different login loading screens right now and users can interact with them.
Website updated.
Updates on the admin panel:
App information: added live charts for CPU, temperature, and RAM
User control: admins now can add/delete/change users directly from this tab, instead of only from command line.
Minor change
Bug fix
FIx bugs due to login page caused server not loading
Add 1s delay in javascript after login to resize the page so the dashboard can be displayed normal.
Fix a table rendering bug in workflow cwl step markdown text.
Changes in version 1.1.30
Major change
new spsAccount class. This class is associated with login management , which allows users to create/delete user/admin accounts, change password, change roles.
Deprecated the spsPlotContainer class since we rewrite the Canvas feature and move to a separate package {drawer}.
New spsCoreTabReplace, which allows users to overwrite the default core tabs.
A lot more SPS options.
Users can now choose whether to load or not load certain tabs on start, even for default core tabs. Combining the spsCoreTabReplace function, now users can customize everything of the original app.
Users can change the app title, and logo image.
Admin panel added to app. Users now can visit the admin panel by adding “?user_definded_string” to the end of the url. Default is “admin”. Login with an admin account is required. Users can use the spsAccount class to add/change an admin account before starting the app.
App information: a tab displays current SPS app server information, like CPU, RAM, size, etc.
User control: a tab to see account information of current SPS app.
Changed the way to install modules. Default modules, workflow, RNAseq and quick ggplot dependency packages are not installed by default, unless you use dependency = TRUE in installation command. It means all these dependencies are moved from Imports to the Suggests class. This helps to save quite some time on SPS package installation. Users install these packages based on their needs. When users loads these modules but depend packages are not fully installed, app will not crash, instead, a warning message with install instructions will be displayed on both console and app UI.
Based on the module installation change, module loading methods are also changed. Module server functions are only called if users set the option to load them. In previous versions, the server functions are still loaded, just hide the unloaded module UI. This saves a lot of time on app starting time, roughly from > 10s to < 3s if none of the default modules are loaded.
Bug fix
update all links to our new website:
Fix some bugs in the guide system
Changes in version 1.1.20
Major change{.uri}.
Separation of SPS smaller functions into 3 different packages. We hope these packages can help people in their own Shiny app, or other R projects.
{spsComps}: SPS components, all new Shiny custom components and utility functions that are used in Shiny server side.
{drawer}: the redesign of Canvas, purely front-end image editing tool.
{spsUtil}: SPS utilities, general useful utility functions that can be used with/without Shiny.
Redesigned the new tab feature. Now users use spsNewTab function to create their new custom visualization tab. The old newSpsTab function is deprecated. Easier syntax and templates are used. By default it will use the “simple” template which wraps 90% of the shiny code from users so they can focus on the plotting code. There is also the “full” template which expose all the Shiny code to users.
New spsEzUI and spsEzServer functions are used in the “simple” template to wrap complex Shiny code.
New spsOptDefaults, which prints out all the default SPS options and current values of these options on console.
New notification system. Developers can write some notifications which stores in a remote location and when app starts, it will try to download and parse this file to notifications messages to broadcast to users. This way, developers can send messages to users often without re-deploy the app. The notification will appear on the top right corner.
The interactive guide is back. After a few versions of tests, we added the guide system back. This time, developers can customize their own guides. A guide_content.R file is created when a SPS project initialize. It is stored in R of folder relate to the project root. The guide will also be displayed on the app top right corner.
Minor change
Bug fix
fix bugs due to shiny updates to 1.6.0
Fix all bugs caused by {shinydashboardPlus} v2.0 updates.
Changes in version 1.1.10
Changes made from 1.1.0 to 1.1.05
Workflow module R session
RNAseq module
General UI
Workflow module CWL tab
Workflow module fully functioning
Now you can run a full example workflow in SPS by choosing the “Example” option on workflow setup step.
Other systemPipeR preconfiged workflows will cause problems because formatting issues that will cause errors in systemPipeR::runWF function, not introduced by SPS. Please wait the updates on systemPipeR to fix this. You can still use SPS to prepare files for all workflows. That means, step 1-4 will work, step 5 will give you errors if you choose a workflow which is not “Example”.
Rework on the workflow part
All 3 tabs merged into the main tab
changed config tab to CWL tab
added support for the running wf as a sub tab
Now the main tab has 5 subtabs, they are all connected.
Better guidelines for users, step-like usage, can’t reach other steps if a previous step is not completed.
Original snapshot management drop down page changed to running workflow session. This session will lock users to a unique page, they can’t interactive other app parts on the page(working directory changed), to prevent app crash due to wd change.
Other changes
A new UI component spsTimeline : horizontal timeline UI unit, has status, can be updated on server by updateSpsTimeline.
A new UI bsHoverPopover: enhanced high level function of bsPlus::HoverPopover, additional JS used to make the popover work on buttons as well.
Fixed some link problems in renderDesc. Better links in renderDesc, enlarged and spacing animation for links.
Change on about page
The news is now rendered on about tab in the app
reduced developer content on about page.
changed developer emails to github links.
Change on visualization
RNAseq part is now only in one tab as big module: users upload the targets file and a raw count table, and make different plots in subtabs.
This introduced a lot of dependencies, will decide later if we keep as it is or separate it to spsBio.
Changes in version 1.48.0
NEW FEATURES
Function
ri_data_extract allows for a time range for each searched
m/z,
instead of a single range for all masses.
Man-pages typos and clarifications. No more user-significant changes.
BUG FIXES
Add extra assertions on
ncdf4_convert.
The dependency package
ncdf4 should be on
Imports rather than
Depends
on the DESCRIPTION file.
Changes in version 1.31.1
changed default DE estimation method from exactTest to GLM-based test (glmQLFit, glmQLFTest) when using edgeR.
removed DE estimation method for no-replicates dataset.
Changes in version 1.12.0
New features
Minor changes and bug fixes
Changes in version 1.35.1
Changes in version 1.11.1
Changes in version 1.5.1
Changes in version 1.13
Changes in version 1.13.1
Changes in version 1.1.0
Changes in version 1.27.15
Update documentation of geneModelFromTxdb
Changes in version 1.27.14
Add rmarkdown into Suggests
update importScSeqScore.
Changes in version 1.27.13
Fix the size by number when read from file.
Changes in version 1.27.12
add decontructor to hic.cpp.
Changes in version 1.27.10
split the vignette to multiple files.
Changes in version 1.27.9
plot back to back Interaction Data Track
Changes in version 1.27.8
fix the typo in hic.cpp
Changes in version 1.27.7
figure out the error in dyn.load trackViewer.so
Changes in version 1.27.6
add support for .hic and .cool for importGInteraction
Changes in version 1.27.5
add importGInteraction
Changes in version 1.27.4
change the re-sample method for viewTracks
Changes in version 1.27.3
Update documentation.
add label_on_feature for lolliplot
Changes in version 1.27.2
Fix the bug for pie plot of dandelion.plot when introduce label.parameters.
Changes in version 1.27.1
Fix the bug that if all scores are greater than 10 and all scores are integer.
Changes in version 1.5.02 (2021-01-21)
Changes in version 0.99.12
Major changes
Removed top level doc/ folder
Changes in version 0.99.11
Major changes
depends R changed to >= 4.1
Changes in version 0.99.10
Major changes
Changes in version 1.1.2
SIGNIFICANT USER-VISIBLE CHANGES
Separation of only one function into two
Introducing new input data formats to the above functions
Changes in version 0.99.13
No changes
Changes in version 0.99.12
minor bugs fixed
Changes in version 0.99.11
T/F changed by TRUE/FALSE
Changes in version 0.99.10
More evaluated chunks in the vignettes
Changes in version 0.99.9
xlsx files changed to html, library removed
generate_cliques structure has changed, new plot function.
Changes in version 0.99.8
Logfile added to runrewiring method.
Message structure of preparerewiring method has been cleaned.
Changes in version 0.99.7
Rewiring method outputs every supermodule
Changes in version 0.99.6
vignette files are locally available (instead of github)
SummarizedExperiment objects are allowed to use
code style and structure has been improved
Changes in version 0.99.5
openxlsx to xlsx library changed
Changes in version 0.99.4
class() functions removed.
Changes in version 0.99.3
excel_generation function added
vignette file updated
Changes in version 0.99.2
rewiring method part parallelized
Changes in version 0.99.1
vignette file added
minor bugs fixed
Changes in version 0.99.0
automatic modules selection in rewiring test.
rewiring html report file added.
unit tests added.
Changes in version 0.99.0 (2020-12-30)
Changes in version 1.15.6
optimized read.nhx for large tree file (2021-03-12, Fri)
Changes in version 1.15.5
Changes in version 1.15.4
Changes in version 1.15.3
Changes in version 1.15.2
Changes in version 1.15.1
Changes in version 0.99.3
Changes in version 0.99
Initial release.
Added preprint to CITATION, vignette.
Changes in version 1.30.0
Migrated createClusterMST() to the TrajectoryUtils package.
Modified orderCells() to return a more informative PseudotimeOrdering object.
Handle pseudotime matrices in testPseudotime() by testing each path separately. Support inclusion of custom row.data= in each output DataFrame.
Changes in version 0.99.0 (2020-09-30)
Changes in version 1.10.0
Added more tximeta() messaging about specifying the ‘source’ in linkedTxome. Essentially, this triggers GTF processing behavior that users may want to avoid, and so specifying a string other than “Ensembl” may be preferred. Also added note to vignette.
Added note to vignette about alevin import with tximeta where the ‘tgMap’ step requires gene IDs and not gene symbols.
Added hashes for: GENCODE 38 (H.s.), M27 (M.m), and Ensembl 104; GENCODE 37 (H.s.), M26 (M.m), and Ensembl 103; GENCODE 36 and Ensembl 102.
Fixed a bug where multiple parsed Ensembl GTF TxDb would be added to the BiocFileCache with the same rname.
Changes in version 1.9.11
Added hashes for GENCODE 38 (H.s.), M27 (M.m), and Ensembl 104.
Changes in version 1.9.6
Using tools::R_user_dir instead of rappdirs, in line with changes in BiocFileCache..
Changes in version 1.9.5
Added hashes for GENCODE 37 (H.s.), M26 (M.m), and Ensembl 103.
Changes in version 1.9.2
Changes in version 1.19.4
Changes in version 1.1.9
Allow selection of number of reads to load from FastQ file in prep and split functions. Default: 1M reads (1e9).
Minor fixes BiocCheck.
Changes in version 1.1.8
Use
query_regions to select the restriction fragments to use for
differential
testing in
diffWaldUMI4C.
Changes in version 1.1.7
Fixed bug with limits of the log2 OR values when plotting differential windows.
Changes in version 1.1.6
Fixed bug in creation of gene annotation when an exon belongs to more than one transcript.
Fixed bug when only one sample is provided (no name in assay columns).
Changes in version 1.1.5
Fixed bug in selection of reference UMI4C sample when more than 1
sample
has the same number of total UMIs. Now it will select the first one.
The selection of sample to use as reference can be overriden by the
ref_umi4c argument.
Changes in version 1.1.4
Fixed bug in domainogram plotting where white color was not aligned with 0 log2 FC.
Changes in version 1.1.3
Fixed bug when providing a reference sample to use for normalizing UMI counts.
Changes in version 1.1.2
Fixed bug when
cut_pos!=0 that generated a gap in the digested
genome
object (see issue #8)
Changes in version 1.10.0
NEW FEATURES
A new data structure, universalmotif_df, has been made available. This allows for motifs to be manipulated as one would a data.frame object. The to_df() function is used to generate this stucture from lists of motifs. The update_motifs() function is used to apply changes to the actual motifs, and to_list() returns the actual motifs. Note that this is only meant as an option for more conveniently manipulating motif slots of multiple motifs simultaneously before returning them to a list; the universalmotif_df structure cannot be used in the various universalmotif functions. Additionally, requires_update() can be used to ascertain whether motifs are out of date in a universalmotif_df object. Many thanks to @snystrom for discussions and significant contributions.
view_motifs(): the universalmotif package now relies entirely on its own code to generate the polygon data used by ggplot2 to plot motifs, meaning the ggseqlogo import has been dropped. A number of new options are now available, including plotting multifreq logos and finer control over letter spacing. An effort has been made to ensure that the default behaviour of the function be unchanged from previous versions. This change should also allow for easier fixing of bugs and flexibility for future additions or changes.
New function, merge_similar(): identify and merge similar motifs in a list of motifs. Essentially, a wrapper around compare_motifs(), hclust(), cutree(), and merge_motifs().
New function, view_logo(): plot logos with matrix input instead of motif object input. Arbitrary column heights and multi-character letters are allowed.
New function, average_ic(): calculate the average information content for a list of motifs.
trim_motifs(…, trim.from): trim from both directions or just one.
shuffle_sequences(…, window, window.size, window.overlap): shuffle sequences iteratively in windows of specified size.
scan_sequences(…, return.granges): optionally return a GRanges object.
scan_sequences(…, no.overlaps, no.overlaps.by.strand, no.overlaps.strat): remove overlapping hits after scanning, preventing overlapping hits by the same motifs from being returned. This can optionally be done per strand. Either the first hit or the highest scoring hit can be preserved per set of overlapping hits. These new arguments can also be used in enrich_motifs().
scan_sequences(…, respect.strand): whether to scan the sequence strands according to the motif strand slot. Only applicable for DNA/RNA motifs. This option is also available in enrich_motifs().
MINOR CHANGES
Some additions and clean-up to documentation and vignettes.
Support for MotIV-pwm2 formatted motifs has been dropped, as the package is no longer a part of the current Bioconductor version.
read_matrix()/write_matrix(): the sep argument can now be NULL (no seperators.)
The Rdpack dependency has been dropped.
merge_motifs(): single-motif input now simply returns the motif instead of throwing an error.
view_motifs(…, dedup.names): now TRUE by default. Furthermore, the make.unique() function is now used to deduplicate names.
compare_motifs(…, method): the default comparison method has been changed back to PCC.
BUG FIXES
Using create_motif() with a single character no longer throws an error.
Generating random motifs with filled multifreq slots now works.
Changes in version 0.99.0 (2018-05-15)
Changes in version 1.2.5 (2021-02-14)
Changed package name to VaSP from vasp.
Changes in version 1.2.1 (2021-01-16)
Added the citation and improved some codes.
Changes in version 1.1.6
Move sanity check vignette to inst/.
Changes in version 1.1.5
Add Michael Stadler to package authors.
Changes in version 1.1.4
Fix typo in documentation.
Changes in version 1.1.3
Add vignette subdirectory with sanity checks.
Changes in version 1.1.2
Add functions plotVelocity and plotVelocityStream.
Changes in version 1.1.1
Refresh cached environments.
Changes in version 1.1.0
Bioconductor release 1.1.0.
Changes in version 0.99.0
Changes in version 0.99.8 (2021-05-07)
Changes in version 3.13.8
Fix plotQC() for XCMSnExp objects
Changes in version 3.13.7
Add
featureArea function to extract the m/z-rt region for features.
Fix
featureSpectra function.
Re-add the LC-MS/MS vignette.
Feature: plotQC() supports XCMSnExp objects now
Changes in version 3.13.6
Fix issue #545: skip second centWave run with CentWavePredIsoParam in regions of interest with undefined peak boundaries/scan ranges.
Temporarily remove the LC-MS/MS vignette (until MsBackendMgf is added to Bioconductor).
Changes in version 3.13.5
Add
filterChromPeaks method to filter chromatographic peaks in a
XChromatogram or
XChromatograms object.
Add
filterChromPeaks method for
XCMSnExp (issue #541).
Support return of
Spectra objects by
chromPeakSpectra,
featureSpectra
and
reconstructChromPeakSpectra.
Support extraction of MS1 spectra with
chromPeakSpectra.
Support extraction of the spectrum with the largest total signal or
largest
base peak signal in
chromPeakSpectra.
Add support for extraction of spectra for selected/individual
peaks/features
using the
peaks and
features parameter in
chromPeakSpectra and
featureSpectra, respectively.
Changes in version 3.13.4
Import
Param object from
ProtGenerics.
Import
filterIntensity,
normalize and
alignRt for
Chromatogram and
MChromatograms from
MSnbase.
Changes in version 3.13.3
align,Chromatogram gains new method
"none" which will only keep
values
with identical retention times. For
method = "matchRtime" the (much
faster)
matching function
closest from the
MsCoreUtils package is used.
Method
correlate,Chromatogram gains parameter
useIntensitiesAbove
to
perform the correlation only with values larger than this threshold
(avoiding thus high correlation because of many 0-values).
Add method
filterIntensity,Chromatogram that allows to filter a
chromatogram
object keeping only data points with an intensity above a user
provided
threshold.
Changes in version 3.13.2
Add new function
manualChromPeaks allowing to manually add and
integrate
chromatographic peaks.
Changes in version 3.13.1
Support subsetting of
XChromatograms with
drop = FALSE.
Changes in version 1.17.2
We provide a new function LCD_extractCohort_callPerPID() which also belongs to the LCD family and which performs the detection of signatures at cohort-wide level, but re-runs the actual computation of the exposures per-PID with only the signatures identified in the cohort-wide calling. The ovall wrapper function LCD_complex_cutoff_combined() now also calls the new function and stores the result in the returned list with item name extractCohort_callPerPID
Changes in version 1.17.1
Introduction of an input parameter minimumNumberOfAlterations for the functions LCD_complex_cutoff_perPID(), LCD_complex_cutoff_consensus() and LCD_complex_cutoff_combined(). If a sample has less mutations than this cutoff, a warning is issued. By default, this values is set to 25 and may be a good choice for analysis of SNV mutational signatures. For analysis of Indel mutational signatures, a better choice is 20.
Changes in version 1.2.0
Update anndata and other Python dependencies, now using anndata v0.7.6
Improved conversion checks for all slots in AnnData2SCE()
Enable return conversion of the varm slot in AnnData2SCE()
Avoid converting obsp and varp to dense matrices in AnnData2SCE()
AnnData2SCE() should now always return dgCMatrix matrices when assays are sparse
More consistent conversion of metadata to uns in SCE2AnnData()
Handle conversion of list columns in colData and rowData in SCE2AnnData()
Better support for converting anndata SparseDataset arrays
Improved support for conversion of HDF5 backed AnnData objects
Better support for writing DelayedArray assays in writeH5AD()
Store X_name in AnnData2SCE() for use by SCE2AnnData() and add an X_name argument to AnnData2SCE() and readH5AD()
Add a compression argument to writeH5AD()
Export zellkonverterAnnDataEnv for use by other packages
Changes in version 0.99.3
NEW FEATURES
Changes in version 2.16.0
Changes in version 3.0.0
curatedMetagenomicData now contains 20,283 samples from 86 studies
A total of 10,084 samples added since Bioconductor 3.10 (October 2019)
Studies added since Bioconductor 3.10 (October 2019):
The
curatedMetagenomicData() method has been refactored for efficiency
mergeData()method has been refactored for accuracy and efficiency
returnSamples()method has been added for returns across studies
sampleMetadataobject replaces the
combined_metadataobject
combined_metadataobject will be removed in the next release
A number of methods have moved directly to defunct status:
cmdValidVersions()
getMetaphlanTree()
ExpressionSet2MRexperiment()
ExpressionSet2phyloseq()
All named accessors (e.g.
HMP_2012.pathcoverage.stool()) have become defunct
curatedMetagenomicData()method replaces all named accessors
Changes in version 1.14.0
New features
The version argument now allows users to select either 1.1.38 or 2.0.1.
Version 2.0.1 includes RNASeq2Gene data as RSEM TPM gene expression values (#38, @mherberg).
Genomic information updated for RaggedExperiment type data objects where ‘37’ is now ‘GRCh37’ (#40, @vjcitn).
Datasets (e.g., OV, GBM) that contain multiple assays that could be merged are now provided as merged assays (#27, @lwaldron).
The vignette now includes sections on how to use the TCGAprimaryTumors and getWithColData functions.
Bug fixes and minor improvements
Changes in version 1.5.1
crispr,
copyNumber,
TPM,
mutationCallsand
metadatadatasets. Newer versions for the other datasets were not released.
Changes in version 0.99.0
Changes in version 1.3.2 (2021-03-09)
Added pancancer regulons for application in cancer.
Changes in version 1.3.1 (2021-02-08)
Fixed bug in Seurat’s related unit tests due to Seurats package update to version 4.0. s@assays$dorothea@misc is now list(), before it was NULL.
Changes in version 0.99.0
Changes in version 0.99.11
Changes in version 1.8.0
Other notes
Changes in version 0.99.9 (2021-04-20)
Added data from Zanotelli et al. Mol Syst Biol 16:e9798(2020)
Changes in version 0.99.8 (2021-04-15)
Allow on disk storage of images and masks
Changes in version 0.99.7 (2021-03-24)
Improved documentation
pkgdown website
Changes in version 0.99.6 (2021-03-23)
Added data from Jackson, Fischer et al. Nature 578,615–620(2020)
Changes in version 0.99.0 (2020-11-12)
Extended vignette
Added function documentation
Added dataset documentation
Formatted the package for Bioconductor submission
Changes in version 0.1.0 (2020-11-02)
Initial commit
Creation of the imcdatasets package
Added the damond-pancreas-2019 dataset
Changes in version 0.99.3
Add human PBMC data
Add LRcell related information in vignettes
Changes in version 0.99.2
change dependency back to R >=4.1
R>=3.6 triggers warning
Changes in version 0.99.1
change dependency to R >=3.6
Changes in version 0.99.0
version 0.99.0 released
Submitted to Bioconductor
Changes in version 0.99.0 (2021-01-21)
Changes in version 0.99.5 (2021-04-21)
Changes in version 0.99.0
Changes in version 0.99.8 (2021-04-08)
ptairData Watched Tags added to Bioconductor Support Site User Profile
Changes in version 0.99.7 (2021-04-01)
extended description
added BugReports to description files
completed NEWS file
added inst/script/script.R
added section installation and sessionInfo to the vignette
Changes in version 0.99.0 (2021-03-05)
Submitted to Bioconductor
Changes in version 1.29.2
Suggest rpx version 1.99.2 or later (to make use of caching and avoid repeated downloads).
Remove the shinyMA function.
Delete the code from the rTANDEM section, and only mention the package.
Remove synapter(data) suggestion.
Changes in version 1.29.1
Specify MSnID::peptides() (see also).
Changes in version 1.5.1
Changes in version 0.99.3
Added
liang2020_hela datasets <2020-04-23>
Changes in version 0.99.2
Removed remaining tilde (U+223C) in man pages <2020-01-09>
Changes in version 0.99.1
Removed tilde (U+223C) in man pages <2020-01-09>
Changes in version 0.99.0
Changes in version 2.6.0
Added the Bacher T cell dataset.
Added the Bhaduri organoid dataset.
Added the Darmanis brain dataset.
Added the Ernst spermatogenesis dataset.
Added the Fletcher olfactory dataset.
Added the Giladi HSC dataset.
Added the He organ atlas dataset.
Added the Jessa brain dataset.
Added the Nowakowski cortex dataset.
Added the Pollen glia dataset.
Added the Zeisel nervous system dataset.
Added the Zhao immune liver dataset.
Added the Zhong prefrontal cortex dataset.
Added the Bunis HSPC dataset (Dan Bunis).
Changes in version 0.99.1 (2021-03-05)
Changes in version 1.4.0
New features
SingleCellMultiModal function allows the combination of multiple multi-modal technologies.
GTseq data from Macaulay et al. (2015) now available (@lgeistlinger)
SCoPE2 data from Specht et al. now available thanks to @cvanderaa (#26)
scMultiome provides PBMC from 10X Genomics thanks to @rargelaguet
Bug fixes and minor improvements
Metadata information (function call and call to technology map) included in SingleCellMultiModal
scNMT includes the original call in the MultiAssayExperiment metadata
Improved and edited Contributing Guidelines for clarity
Changes in version 1.3.19
SIGNIFICANT USER-VISIBLE CHANGES
spatialLIBD has been updated to work with SpatialExperiment version 1.1.701 which will be released as part of Bioconductor 3.13. This changes internal code of spatialLIBD which will work with any objects created with SpatialExperiment version 1.1.700.
Changes in version 1.3.16
SIGNIFICANT USER-VISIBLE CHANGES
The citation information has changed now that spatialLIBD has a bioRxiv pre-print at.
Changes in version 1.3.15
SIGNIFICANT USER-VISIBLE CHANGES
We now use plotly::toWebGL() to make the web application more responsive.
Changes in version 1.3.14
SIGNIFICANT USER-VISIBLE CHANGES
The documentation and help messages shown in the web application have been revamped and improved.
Changes in version 1.3.12
NEW FEATURES
We added a new vignette that shows how you can use spatialLIBD with any 10x Genomics Visium dataset processed with spaceranger. The vignette uses the publicly available human lymph node example from the 10x Genomics website.
Changes in version 1.3.3
NEW FEATURES
Overall the package has been updated to use SpatialExperiment version 1.1.427 available on Bioconductor 3.13 (bioc-devel). Several functions were re-named such as sce_image_gene_p() now has a shorter name vis_gene_p(). This update also changes these visualization functions to ONLY support SpatialExperiment objects instead of the original modified SingleCellExperiment objects.
Updated citation information to reflect that is now public. Also added a link on the README to for the manuscript high resolution images.
Changes in version 0.99.0 (2021-03-28)
Changes in version 0.99.0
Changes in version 1.1.2
Data is now hosted on FigShare.
Added new datasets: GSE150430, GSE154778, GSE125969, GSE134520, GSE123366
Changes in version 1.1.1
Now uses BiocFileCache to download data.
Changes in version 0.99.11
Sixty Five software packages were removed from this release (after being deprecated in Bioc 3.12): adaptest, ArrayTV, BioSeqClass, CHARGE, chimera, CNVtools, CorMut, DESeq, explorase, flowFit, flowSpy, flowType, focalCall, FourCSeq, FunciSNP, GeneticsDesign, GenRank, GGBase, GGtools, GOFunction, gQTLBase, gQTLstats, hicrep, ImpulseDE, ImpulseDE2, joda, JunctionSeq, LINC, Logolas, mcaGUI, metaArray, metaseqR, methVisual, methyvim, Mirsynergy, MmPalateMiRNA, MOFA, MotIV, NarrowPeaks, netbenchmark, netReg, OGSA, OmicsMarkeR, pathprint, PathwaySplice, PGA, PGSEA, plrs, prada, Prize, Rariant, reb, Roleswitch, rTANDEM, sapFinder, scsR, shinyTANDEM, sigaR, signet, simpleaffy, spotSegmentation, Starr, SVAPLSseq, TxRegInfra, xps
Forty nine software are deprecated in this release and will be removed in Bioc 3.14: AffyExpress, affyQCReport, AnnotationFuncs, ArrayTools, bigmemoryExtras, BiocCaseStudies, CancerMutationAnalysis, CexoR,, IntramiRExploreR,
Fourteen experimental data packages were removed this release (after being deprecated in BioC 3.12): flowFitExampleData, FunciSNP.data, geuvPack, geuvStore2, GGdata, methyvimData, mitoODEdata, Mulder2012, pathprintGEOData, pcaGoPromoter.Hs.hg19, pcaGoPromoter.Mm.mm9, pcaGoPromoter.Rn.rn4, waveTilingData, yriMulti
Eleven experimental data packages are deprecated in this release and will be removed in Bioc 3.14: ceu1kg, ceu1kgv, ceuhm3, cgdv17, dsQTL, facsDorit, gskb, hmyriB36, JctSeqData, MAQCsubsetAFX, yri1kgv
Fourteen annotation packages were removed from this release (after being deprecated, MeSH.Eco.55989.eg.db, MeSH.Eco.ED1a.eg.db, MeSH.Eco.IAI39.eg.db, MeSH.Eco.UMN026.eg.db, MeSH.Eqc.eg.db
Eighty seven annotation packages are deprecated in this release and will be removed in Bioc 3)
No workflow packages were removed in this release.
One workflow package is deprecated in this release to be removed in 3.14: eQTL | http://bioconductor.org/news/bioc_3_13_release/ | CC-MAIN-2021-43 | refinedweb | 32,481 | 52.15 |
Visual Studio is my main development environment. I’ve been using this tool probably since version 2003…2005. I am really happy that VS is getting more and more powerful these days and you can also use it on multiple-platforms (through VS Code, for web or cloud apps). What’s even better - it’s free for personal use or if you’re a small company (Community Version)! Today, I’ve prepared some productivity tips that might make your life a bit easier when developing an app in this Microsoft IDE.
I target native app development, but most of the rules should be generic to other languages as well.
- Learn how to move in code
- Learn shortcuts
- Enable enhanced scroll bar
- Install addons
- Exercise
- Summary
- Your turn
Learn how to move in code
This is a very broad topic and probably the most important aspect on my list. When you learn programming you might work with simple projects with just several code files. In that scenario you have most of the code in your head. But, in a commercial projects you will end up with hundreds of files and classes. How to move efficiently is such complicated structures? You can easily forget about file hierarchy, let alone classes and subsystems.
Here are some basic steps:
Use go to definition/declaration
Probably, this is what I use the most often: switching between definition and declaration of a function, a variable or a class.
While you’re reading some code inside a method just by clicking on the method name
(F12, Ctr+Alt+F12) you can go to its declaration or vice versa. Then, you can see where the function/method header is located, what class it’s part of.
This works not only for methods or types, but also for variables/members: in a long method, you can just go to definition of some variable to see where it’s declared.
Possible problem: sometimes this feature does not work well for large projects :) Intellisense is from time to time stubborn and does not want to cooperate. But if you’re patient you’ll reach the target eventually. Also Intellisense is greatly improved with each version of Visual Studio.
Navigate to symbol
The most powerful thing: being able to navigate to anything you like. Maybe you want to check a function? or a class declaration? or some other symbol? In Visual Studio (Starting from version 2010) there is “Navigate To” command:
Ctrl + COMMA
Enter the short-cut and then start typing a symbol name you want to check. VS will dynamically look for it and will give you a list of found items. You can easily navigate to a particular line in the code.
More about Navigate To:
I use that kind of navigation frequently. Sometimes I want to find something, but don’t know the proper type name. In that case I start typing some possible words that should match and usually I find what I was looking for.
In VisualAssist (described in the Plugins section) there is even more powerful tool: Find Symbol in Solution. This windows lets you quickly find any symbol in the solution, you can use prefixes, negative filters, multiple strings, etc.
See all references
This feature is very handy if you know what type/method you are looking for and you want to see where it’s being used. You can explore examples and recreate them in your solution.
At work, I often use this to track all the places that are related to some type/symbol. For example, when I need to add a similar type (some kind of a new attribute for a graphical element) I can search for all occurrences of some existing type and do the same for my new type: like recreate initialization, add to lists of supported types, register in UI, etc.
Recently, I’ve noticed that it might be nice to get something like “find some references”. This would be handy if you know that a function/code is used in hundreds of places (so search times might be huge), but you’re actually interested in any appearance, only a few would satisfy. This would work much faster. On the other hand, the IDE doesn’t know what items are most valuable to you… so it’s safer to return all the occurrences.
You might be also interested in using View Call Hierarchy feature, that shows calling hierarchy better that just finding all references.
Navigate backward/forward
Unfortunately, I must admit, I don’t have large RAM in my head and I constantly forget where was I two minutes ago in the project :) Luckily, I can navigate backwards and forwards to previously visited places -
Ctrl+ - and
Ctrl + Shift + -!
Alternatively, if you’re doing changes in two files, you can switch between them by using
Ctrl+Tab. This will show the list of recently used and open files so you can open it immediately.
There are also bookmarks that can be leveraged. You might mark important places of the code and switch between those places. Still, I don’t use them much often. Moving back and forth to recently visited places seems to be creating sort of natural bookmarks and you don’t have to remember additional shortcuts. On the other hand using bookmarks might be a good exercise.
Other tools
- View Call Hierarchy - Finding all references of a function might be ok, but VS offers more advanced feature: Call Hierarchy. This shows what other functions called your original method.
- Class Hierarchy - Handy when you want to track what are the derived classes from you given class, or you want to track the common root of types. This feature is also connected to Object Browser.
- Switch between header and implementation file - another basic tool -
Ctrl+K, Ctrl+O. Especially useful when you write implementation of a class, and want to go to class declaration.
// TODO- Task List, mark important places in the code with
// TODO: textand then you can see them in Task List Window.
Learn shortcuts
Bookmark one one this pages:
- MSDN Pre-defined Keyboard Shortcuts VS 2015
- Visual Studio 2015 keyboard shortcuts
Print it, keep it near your desk and learn those shortcuts daily.
Enable enhanced scroll bar
Every time I return to a simpler IDE that hasn’t enhanced scroll bar feature I am a bit lost. Enhanced scroll bar adds a huge boost to the way you can move in a file. In simple cases, you might remember where your method is located: is it at the beginning, near the middle or at the end of a file… that might work for some time. But the advanced scroll bar adds a map where you can find your code much faster. It creates a bigger picture and thus your brain can memorize where the code is ‘visually’ located in a file. No more random scrollbar searches! :)
Since most of lines have like 80…120 characters and you probably use a monitor with wide aspect ratio, then you should have some space on the right/left side in the editor. So even if you use very wide scrollbar it shouldn’t decrease the space for the code itself.
Also, the scrollbar shows some additional information like last modification, breakpoints, compiler errors and of course where is the currently edited line.
Read more about enhanced scroll bar at MSDN blog
Note that it’s great to have relatively small files. Otherwise your scrollbar map will just look like a normal, almost one colour, bar:
There is a chance to still get some value of such map, but the shorter the file the better in my opinion.
In Productivity Tools For VS2013 there is a addition called “Structure Visualizer”. With “Show code structure in the margin” option you’ll get a nice visualization of code blocks in a file.
Above image comes from official plugin site: visualstudiogallery/Productivity Power Tools 2013
Install addons
Visual Studio is a very decent environment, but what if we could do better? Look for plugins that help with your daily tasks and fills some of the gaps that VS has.
VisualAssist
VisualAssist from Whole Tomato Software
I am a great fan of VisualAssist. For example, you can read some of my tips for this tool in my post from 2014: 3 Tools to Understand New Code from Visual Assist . VA is a complete set of tools for refactoring, code navigation, coding assistance… even debugging. Or to write this shortly: set of productivity tools.
Just take a look here:
It’s hard to tell when I am not using VA features - because it’s enabled all the time. But things like renaming a symbol name, extracting a method, class, documenting a function header, finding symbols, find base method declaration, class hierarchies… all of that are natural and really handy with VA. Also I am really impressed with the performance, rarely I need to wait for the results. As I mentioned before, you often need to wait for Intellisense, but with VA you don’t see such situations.
It’s not free (279$ for the full licence, 99$ for personal, 49$ for academic), but I highly encourage to save some money and buy the extension.
You can download the trial and have a quick look: Download a free trial.
ReSharper for C++
ReSharper For C++ by JetBrains
I’ve never used it, but always wanted :) I need to allocate some time and experiment with the trial version.
Resharper is a well known extension for .NET developers, but eventually the company was able to produce similar version for C++! It’s also a really large set of productivity tools.
BTW: here is the comparison (made by JetBrains): VisualAssist vs ReSharper for C++
In terms of pricing you can use several models, for example € 199.00 for first year, € 159.00 second, … or use some discounts.
Productivity Power Tools for VS
Productivity Power Tools 2013
Productivity Power Tools 2015
This time it’s a completely free set of tools that highly improve work with VS. Even if you have Visual Assist or ReSharper the plugin can still bring some value.
Here is the full list of features:
- Peek Help
- Solution Explorer Errors
- Structure Visualizer
- Double click to maximize windows
- Timestamp margin
- Quick tasks – Edit Present On
- Ctrl + Click to Peek Definition
- HTML Copy improvements
- Recently Closed Documents
- Match Margin
- Power Commands context menu cleanup
- Syntactic Line Compression
- Quick Tasks
- Power Commands
- Color printing
- Middle-Click Scrolling
- Organize Imports for Visual Basic
- Custom Document Well
- Tools Options Support
- HTML Copy
- Fix Mixed Tabs
- Ctrl + Click Go To Definition
- Align Assignments
- Column Guides
- Colorized Parameter Help
I especially like: Scrollbar markers (that shows additional code structure on the scrollbar), Recently Closed Documents, Document Tabs and some of the power commands.
Other interesting plugins
- AnkhSVN - Subversion Support - khSVN open source (free) Subversion SourceControl Provider.
- C++ Quick Fixes - VS 2015 only, add some help (in context menu) to fix some of the basic coding errors (like missing include, semicolon, using namespace, etc).
- VS10x CodeMAP - displays a graphical nested representation of the current code editor window (C#, VB, C++).
- Viasfora Add color to your Visual Studio Text Editor!
- Image Watch - Provides a watch window for visualizing in-memory images (bitmaps) when debugging native C++ code.
- DoxygenComments - extension that highlights Doxygen documentation tags inside C++, C# and JavaScript comments.
- Visual C++ Refactoring - VS 2013 only, in VS 2015 more refactoring features were added.
- GraphicalDebugging - VS 2015 only, the extension allows to view graphical representation of variables, e.g. Boost.Geometry models.
- CodeMaid - an open source Visual Studio extension to cleanup and simplify our C#, C++, F#, VB, PHP, PowerShell, R, JSON, XAML, XML, ASP, HTML, CSS, LESS, SCSS, JavaScript and TypeScript coding.
- IncrediBuild - IncrediBuild speeds up builds by distributing C#, C/C++ compilations and other tasks across machines in the local network.
Some more suggestions in this old StackOverflow question: Recommended add-ons/plugins for Microsoft Visual Studio
Exercise
Like with every other tool practice is needed. Usually, after some time you’ll get used to any IDE and you find your own ways to be relatively productive. Still, this doesn’t mean it’s end of the story. Why not testing some other embedded tools, other techniques, key shortcuts, plugins, etc, etc… ?
Here are some suggestions for additional exercises for VS IDE:
- Try to minimize mouse usage, do most of the stuff using only keyboard.
- Learn one keyboard shortcut a day/week
- I mention that I don’t use bookmarks, but as an exercise I could use them for a day or two and then decide if it improves my workflow or not.
- Install ‘deep/large’ plugins like VisualAssist or ReSharper for C++ and (even trial versions) and play with them. Learn what tools and techniques do such plugins bring to the IDE.
- Use some other IDE! Do your pet project in some other IDE like QT Creator, Eclipse, etc, etc… or even use a command line + Vim. Maybe you’ll learn something that can be used in Visual Studio later?
Summary
Visual Studio is a very powerful IDE and it might be relatively hard to leverage all of its features. I hope that thanks to this article you’ve learn some techniques that will help when you work in the IDE. Since writing and reading code is probably the most often activity I think that ‘moving in code’ features are crucial to know. If you can quickly jump between files, locate classes, track variables, go to method definitions… (all via keyboard short-cuts of course! :)) then you can more focus on the actual job and not the problems with the tool.
I didn’t cover a lot of things: like build options, debugging, refactoring, windows layout, themes… maybe those are good topics for other articles. Let me know what would you like to read more.
Your turn
- What are your tips for Visual Studio?
- Do you use some additional tools to work with this IDE?
- What is the most disappointing feature of VS? | http://www.bfilipek.com/2016/04/visual-studio-productivity-tips.html | CC-MAIN-2018-05 | refinedweb | 2,340 | 61.06 |
une 2004
Filter by week:
1
2
3
4
5
Partitioned view can not be updated
Posted by Mike Torry at 6/30/2004 6:56:01 PM
When try to update partitioned view, I get error: The view cannot be updated because its disallowed construct. Why this happen? How to fix it? Thanks for reply. -Mike Torry...
more >>
Import Performance Monitor file (TSV)
Posted by Mike P. at 6/30/2004 3:30:00 PM
I am trying to import the performance monitor file (TSV) into a SQL Server table. The performance monitor file is in the TSV format. When I try to import the data into the table listed below I received the following error: The number of failing rows exceeds the maximum specified tran...
more >>
How to: define and run a DTS package with connections as passed in arguments
Posted by thegriff at 6/30/2004 3:13:32 PM
I have a simple dts task. I need to update tables from a source_server to a target_server. Task: Drop table from target_server then copy table from source_server to target_server. Problem: I want to be able to pass in the source_server and target_server names as arguments. How can I d...
more >>
Newbie to DTS - could use some help
Posted by Jesse O at 6/30/2004 2:45:14 PM
I have a single table called customer, which has new records added daily and also existing records being modified daily. I'd like to bring the table over once a day after midnight, however I'm running into a problem since there are two things I'd like to do, insert records and update records....
more >>
DTSrun with variable
Posted by Sumbody at 6/30/2004 12:55:22 PM
Hi All, I finally got the DTS run to work with my new package thanks to Allan Mitchell.... Now my question is this: How do I pass the Dtsrun command line a variable? EXEC xp_cmdshell 'dtsrun /Ssomesql /Usa /Ppass /NTEST /AMyVar:8=Mydata' The above line works great as long as I hard c...
more >>
DTS Workflow Question
Posted by Kirk at 6/30/2004 12:09:02 PM
I am using SQL Server 2000 and I am writing a DTS package that loops through a recordset and calls another package which does some work based upon passed values. It works and loops great unless the called package fails (which it can since it is connecting to an external server). What I want to do is...
more >>
Error setting global variable in DTS ExecuteSQL
Posted by ED P at 6/30/2004 11:26:10 AM
I'm relatively new to DTS and am having what seems like a very basic problem. I have simplified what I am trying to do down to the following: I create a global variable called gvRosterID as an int with a default value of 10. Then I create a connection and then and an associated ExecuteS...
more >>
DTS Non-GUI install?
Posted by FLX at 6/30/2004 10:55:17 AM
I need install DTS package prpgammatically, without using Enterprise Manager. Is it possible to generate script for an existing DTS package and install it on another server using this script? If not, is there any utility that will allow me to do it? Just like dtsrun? I know I can use dtsrun...
more >>
Don't see what you're looking for? Search DevelopmentNow.com.
Generate script for DTS package?
Posted by FLX at 6/30/2004 10:50:19 AM
1. Is it possible to generate the install script for a DTS package and install it on another server by running the scripts generated, just like creating tables, stored procedures? 2. I know I can use "dtsrun" to execute a DTS package saved as a COM-structured storage file. Is there any similar...
more >>
"Identity column does not allow nulls"
Posted by dan at 6/30/2004 8:15:02 AM
SQL Server 2000 on Windows XP. I try to copy data from an Excel file to a table using a DTS Transformation Task. The PK of the table is CompanyID, declared int and identity. In Transform Data Task Properties | Options, "Enable identity insert" is checked. However, the transformation fails wi...
more >>
Transfer Master / Detail Data (adding with new identity value)
Posted by redinblack NO[at]SPAM zworg.com at 6/30/2004 12:48:45 AM
Salute, Consider this scenario : I have a master/detail database, and another database with the same schema but different data. Now, how can I ADD the master/detail data from the second DB to the first one ? how can I resolve the identity conflict ? If I...
more >>
DTS Package variable
Posted by DJohnson at 6/29/2004 4:18:31 PM
Hi All and tia for your help. I need to create a DTS package that can accept a parameter... The package will be exicuted from stored proc or T-SQL statement. I am thinking dtsrun. My question is how would I create a package that expects a parameter, then how would I call it? The para...
more >>
cross database query in active x script
Posted by Chris at 6/29/2004 1:35:02 PM
Hi, I have an active x script in a DTS package. It has access 2 to global variables in the package. sql = "UPDATE tblplanlines SET tblplanlines.description = mastermap.dbo.tblstppdesc from tblplanlines INNER JOIN " & _ "mastermap.dbo.tblstppdesc ON tblPlanlines.PPLAN = mastermap.dbo....
more >>
Data Extraction for a datamart
Posted by Joe Mong at 6/29/2004 1:33:59 PM
I'm extracting data into SQL Server 2000 from Progress 9.1. Doing it serially is too slow. I tried to multithreading the extract process but ended up with less data without any error message. Is there a possible way of speeding up my extraction without losing data? *** Sent via Devdex htt...
more >>
Importing a specific Excel Sheet From a DTS Package
Posted by Thomas at 6/29/2004 10:10:01 AM
Hey All, I am trying to figure out how to Import a specific Excel sheet in an ActiveX Script set conTextFile = pkg.Connections("Microsoft Excel 97-2000") conTextFile.DataSource = DTSGlobalVariables("gv_FileFullName").Value DTSGlobalVariables("gv_sheet").Value = GetSheet() But i don't kno...
more >>
Import Text Files
Posted by shenshiji NO[at]SPAM hotmail.com at 6/29/2004 9:44:20 AM
I am trying to import a text file to a table in SQL Server. It looks normal at the beginning. After I chose "Fixed Field" - File type: ANSI, Row Delimiter: {CR} {LF}, then click Next, it became misAligned. I could not continue import. I tried different Row Delimiter, none of them workin...
more >>
Output with todays date
Posted by Anup at 6/29/2004 9:28:13 AM
I want to create an excel file through a DTS and stored procedure and the file name should be named as todays date. Anyone have any idea where do i put it or methods to do it. Thanks in advance ...
more >>
DTS Transactions
Posted by GayeF at 6/29/2004 3:30:02 AM
Hi, I have a database with a number of temporary tables. The data in these temporary tables need to be transferred into tables in the same database. There are 5 transformations in all. I need to use transactions in the DTS job becasue if one transform task fails then I need to rollback all inserts...
more >>
bcp and triggers
Posted by Systemspecialist at 6/29/2004 2:07:01 AM
Hi all, I have SQL2000 and i try to load data from text file with bcp. Everything works fine, but triggers didn' t fire. I don;t knouw why. When i try to insert data from query analyzer, trigger fired. So, does anybody know , where can be problem? Thanks...
more >>
Open Access DB & Run Macro - How To?
Posted by Pegasus at 6/29/2004 1:45:44 AM
I need to be able to Open an MSAccess 2000 database then run a macro at a scheduled time. I think the best way to do this is through a scheduled DTS package using an ActiveX script but I'm a novice with VB and I just cannot work out the code required. Is there someone out there who can h...
more >>
DTS data turns into null
Posted by JJ Wang at 6/29/2004 1:02:55 AM
hi, I have a sql server 2000 DTS package, that selecting yesterday's data from one of our vendors database (Advantage platform) into our sql server 2000 db, daily process. my select query is like this: SELECT * FROM vendor_table WHERE (DATE = { fn CURDATE() } - 1) Advantage don...
more >>
DTS Import text file
Posted by Mike P. at 6/28/2004 7:23:34 PM
I have SQL Server 2000 Enterprise Edition with SP3A. I have set up a DTS job to import Windows 2000 Advanced Server performance monitor output values from a text file. Connection1 is a text file: E:\Server_dd_yyyymmdd.txt Connection2 is a OLE DB Provider Connection for SQL Server: Pe...
more >>
DTS : SqlServer to Oracle, problem Create Destination Table
Posted by tristant at 6/28/2004 6:22:24 PM
Hi All, I want to transfer data from SqlServer2000 tables into Oracle 9i. I use Transform Data Task, when I specify the destination table, table does not exist yet, and it dts offers to 'Create Destination Table', when I press Create, the script is : CREATE TABLE "Product_Temp" ( "KDPROD" CH...
more >>
Can't create more than 256 partitions?
Posted by FLX at 6/28/2004 5:16:43 PM
I designed a partition scheme which will partition one extremely large table into many partitions (> 256). I want to build a same name view on the top of all these partions so that I don't need change any code in the current system. The queries against the original table can still query against ...
more >>
Job in a package
Posted by Jérémie Gent at 6/28/2004 12:39:55 PM
I'm looking for a solution for my Intranet users (ASP website) to execute jobs on my SQL Server As I don't know all the possibilities of SQL Server, I had thought I could do a DTS package, save it as VB source code, compile it in a .exe application which my ASP page would execute. I've already...
more >>
Suppress Package/Job Failure Report?
Posted by DHatheway at 6/28/2004 9:47:36 AM
I set up a package with a SQL task that may or may not fail (I do a raiserror if it fails). There's a notfication task dependent on the SQL task step that will only fire on a failure in the SQL Task. If the failure path is taken and the notification step works, I consider this a "success." H...
more >>
Error executing a job with SQL Server Agent
Posted by Michael Vardinghus at 6/28/2004 9:38:35 AM
Does anybody know what to do with this one: Unable to determine if the owner (xxx) of job xxx has server access reason. Could not obtain information about Windows NT group/user xxx. SQLSTATE 42000. Error 8198. The owner of the job is set to the specific user - the user is part of a windows ...
more >>
Error while executing DTS job
Posted by haseeb at 6/28/2004 9:28:21 AM
Hi all, I am running a DTS package job which runs on its schedule. The job truncates the destination table and copies data from source. The job runs fine most of the times and at times the job fails with the following error msg in view job history. Please help me to resolve this issue. ...
more >>
Not returning from errors
Posted by Thomas Scheiderich at 6/27/2004 5:07:41 PM
I have a package I am trying to move data from a progress database to our SQL Server 2000 database. I am getting some field size errors from Progress database, which is expected. I have the max error count set to 100. I am passing the error count to an Sql table on completion. The problem...
more >>
Global Variables and SQl Task
Posted by Ian Clare at 6/26/2004 4:11:01 PM
Have a DTS package that uses a Sequence number off a table to insert records into a database using a incremented global variable. Have a sql task that performs various other tasks and want to set the global variable from within the SQL task. The question is, is this possible and how does one d...
more >>
dts transaction
Posted by news.microsoft.com at 6/25/2004 6:03:02 PM
Hi, I am trying to create a dts package to import about 10 tables from access to SQL server using the DTS import and export wizard. I saved the dts package and tried to add a work flow to make sure the person table is inserted first before the other table. But how can I roll back the entire ...
more >>
Help from experienced DTS Gurus
Posted by Chumma Dede at 6/25/2004 1:55:08 PM
Hi, We have several large and complex DTS packages for converting from OLTP to Star schema, and maintaining them on SQL server is becoming quite cumbersome. Additionaly, we have to change the server/db names and other parameters for different client installations and we're currently doing this...
more >>
Modify DTS Package from Visual Basic
Posted by krutyihoriok NO[at]SPAM hotmail.com at 6/25/2004 12:27:51 PM
Hello. I'm trying to find out if it is possible for me to create some sort of a function to automatically modify a DTS package in a given SQL database. For example, I have 4 MS Access databases containing tables that I need to modify slightly and pull into one table in an SQL database. All 4 hav...
more >>
VBScript and G.Variables
Posted by Nexx at 6/25/2004 10:19:19 AM
Greetings everyone, I have a dts package with a dynamic properties task and the typical assortment of sql queries, connections, etc... The dynamic properties task exists to set the properties of various global variables which are to be passed in from the command line. Question, can I set one ...
more >>
Execute Process Task in dts package
Posted by Greg Barnes at 6/25/2004 7:57:16 AM
I am having a problem running bat or cmd files in my dts packages. Whenever I first create a new package which runs a bat file, the package runs fine. However, if I log out of Enterprise Manager or schedule to run the package later, the bat file is never able to run. From what I can tel...
more >>
Automate Importing Daily Performance File into Table
Posted by Dan at 6/25/2004 7:48:52 AM
My server has Windows 2000 Advanced Server as operating system with SQL Server 2000 Enterprise Edition. I would like to create a SQL Server DTS package to automate the import of my daily performance monitor file. My performance monitor file is created daily at 7:00 am with the followin...
more >>
dts loop problem
Posted by aengusd at 6/25/2004 1:53:17 AM
I've created a loop in a DTS, which retrieves connection information from a SQL table and then (is supposed to) populates tables in different Databases. The loop works, but it keeps updating the same DB, rather than updating each of the individual DBs. The connection information seems to be updat...
more >>
FTP Task : Where to specify the ftp site ?
Posted by Newbie at 6/24/2004 11:55:28 PM
I want to send a text file over to a ftp server via ftp. so I use add the File Transfer Protocol Task and I see that it only allows me to specify the source (which I change to Directory since the text file is on my pc) but I don't know how I could enter the IP address of the ftp server ?...
more >>
xp_cmdshell
Posted by Paul at 6/24/2004 8:46:57 PM
Hi, When I run xp_cmdshell in an ActiveX script that is executed within a DTS package, I get the following error... "Type Mismatch : 'xp_cmdshell' " The below line is what I execute .... xp_cmdshell 'open c:\test\blah.bat', no_output I have tried different variants of the above to no a...
more >>
Help desperately needed - UserDefinedFunctions with parameters in ExecuteSQLTask
Posted by Andreas.Bretl at 6/24/2004 3:54:30 PM
Hi all, I try to implement the following in a DTS: Executing a SQL-Task like the following: SELECT ContactExists FROM BrainBase.DBO.IDP_CheckContactID(?) (Table Function) OR SELECT BrainBase.DBO.IDP_CheckContactID(?) (Function) I want to write the result into a Glob...
more >>
Processing AS task
Posted by Michael Vardinghus at 6/24/2004 2:35:33 PM
How come it doesn't tell me if something goes wroing in AS ? The package just looks as is it is till running. When doing the same thing directly in AS i get error information. ...
more >>
Programmatically decrypt stored procedure?
Posted by FLX at 6/24/2004 2:32:45 PM
Does anyone know how to programmatically decrypt the stored procedures (In SQL Server 2000) encryted with the "With Encryption" clause? Thanks a lot, Lixin ...
more >>
Cancelling..
Posted by Michael Vardinghus at 6/24/2004 2:01:30 PM
SQL / AS is great - but one thing annoys me - if I want to cancel a dts task it seems as if it never works...it persists on doing a package till the end and before starting a new package it will cancel and sometimes it just doesn't get back when cancelled. Is there someway to make this better ...
more >>
Column name "X" was not found
Posted by laura.guanchiale NO[at]SPAM unidos.com.ar at 6/24/2004 5:34:01 AM
Hi ! When I execute a DTS from Enterprise Manager the package reported "Column name Col00x was not found". This error happens when I change the source TXT File. Is there a way to configure a "dynamically" mappings cloumns ? Thanks a lot...
more >>
Data Pump Task with stored proc won't work
Posted by pipo1 NO[at]SPAM ilse.nl at 6/24/2004 4:50:14 AM
I have built a stored procedure that returns a result set I want to use in DTS to populate a table, but on the Transformations tab I see no Source columns? The procedure uses data from several tables to populate a temp table, which is then joined to other tables. Nothing very fancy... On th...
more >>
import a text file to SQL server
Posted by CR at 6/24/2004 2:18:01 AM
I have typed to import a text file to SQL server 2000 with MDAC2.8 installed. The text file is with different record width in each row. I use the 'add connection' and choose the data source 'Text File (Source) and my file. In the text file properties, Fixed field, file type: ANSI, Row delimiter:{...
more >>
Lost package info when we use
Posted by Bernard at 6/23/2004 2:09:01 PM
When i use this code Dim objLotDts As New DTS.Package2 objLotDts.LoadFromStorageFile strNomLotDTS objLotDts.SaveToStorageFile vstrNomFichierDTS Set objLotDts = Nothing I lost the comment put in the DTS package and all the task in this...
more >>
Check Connection
Posted by Gary Spence at 6/23/2004 2:30:02 AM
Hello People, I would like to check that I have a valid connection between SQL Server and an AS 400 (200 miles away) before I execute a DTS Package, an ActiveX script would be great, and also how to terminte the package if the connection is down, I'll be executing the package every 10 mins. Much...
more >>
Check connection to db
Posted by YRAG1 at 6/23/2004 2:18:01 AM
Hello People, Can any one tell me how to check if the connection between SQLServer and an AS400 (200 miles away) is enabled using a DTS Package, I want to make sure the connection is there before I execute the package, an ActiveX script would be great, also how can I exit from a DTS package if the ...
more >>
DTS Problem In Importing from Textfile
Posted by vins at 6/22/2004 10:43:02 PM
Hi. I have Sql Server 2000 With Sql SP3 on Win2K. I am Importing Data from Textfiles to a table which has a column of Varchar(512) Thru DTS Package in VB6 but DTS Truncates the Column to 256 Charcters during import. can anyone help me as this is urgent. I have a deadline to meet....
more >>
·
·
groups
Questions? Comments? Contact the
d
n | http://www.developmentnow.com/g/103_2004_6_0_0_0/sql-server-dts.htm | crawl-001 | refinedweb | 3,484 | 71.34 |
I am pretty new in Python and I have a problem which I could not solve with found answers… hopefully someone can help:
I need to get a list of all local maxima of a data-set which is imported from a csv-file.
Values range from 0 to 0.5 or so.
I just need to get a list of those local maxima of one data row (“Werte”, array or “N”, list) to do statistics on them.
This is what I have got:
import numpy as np from numpy import * N = [] file = open('C:/Auswertung/PEE/PEE_L_1_O_130702-1.1.csv', 'r') Probe = file.readline() # lese Inhalt zeilenweise in Listen Header = file.readline() data = file.readlines() for row in data: columns = row.split(";") # Trenne Zeilen bei ';' N.append(float(columns[1])) Werte = np.array([N]) # one try here: only gives me a set of 1s... c = (diff(sign(diff(Werte))) < 0).nonzero()[0] + 1 # local max print(c)
is there anyone who could help me find the right way to do it?
Thank you a lot!
Best answer
I think you are looking for
argrelmax, from
scipy.signal. It gives you the indices of the relative maxima of a 1d array.
from scipy.signal import argrelmax t=linspace(-4,40,1000) y=sin(t) argrelmax(y)[0]
with result
[126 269 412 554 697 840 982]
to get the values, use
y[argrelmax(y)[0]]
EDIT:
notice that it does not count local maxima at the extreme of your domain. | https://pythonquestion.com/post/python-how-to-get-local-maxima-values-from-1d-array-or-list/ | CC-MAIN-2020-16 | refinedweb | 250 | 76.52 |
It is known that in Role Tailored Based environment BEEP C/AL function is not supported.
This simple blog is based on SystemSounds Class from System.Media namespace
My Ingredients :
- NAV 2009 R2 Role Tailored Client
- Windows 7 Enterprise
Hi Duilio,
Thanks for posting this – the code sample is useful! I ran it on my local NAV database (NAV2009 R2) and it works fine but each time it asks me "Your NAV client is trying to run an external component … ". The options are "Allow this time but ask next time", and "Don't allow this time". Is there a registry setting I need to change to get rid of this annoying NAV message?
Thanks,
Chris
Thanks Chris.
I should have answered to this request in the last two comments in this blog
blogs.msdn.com/…/let-nav-speak-with-net-interop-and-nav-2009-r2.aspx
Please, post here if those are useful for you too.
Cheers
Hi Duilio,
That info in the blog post has worked perfectly – thanks a lot!
Cheeers,
Chris | https://blogs.msdn.microsoft.com/nav/2011/06/02/let-nav-beep-with-net-interop-and-microsoft-dynamics-nav-2009-r2/ | CC-MAIN-2017-51 | refinedweb | 173 | 72.46 |
Hello everyone,
I just started learning c++ and I started with creating a programme that gets your wan ip adress.
Just because it covers some basic stuff.
Getting the content of the website works fine. But the parsing doesn't really work. If tried with sscanf, but it didn't work. Also using regex from the boost libraries didn't work. I think it's because that it uses stings and my output is a char.
So if anyone could give me a good and compact way to extract the ip out of the content, it would be very nice.
You can also give me other advice to improve my skills. :)
#include <windows.h> #include <wininet.h> #include <iostream> #pragma comment (lib, "wininet.lib") using namespace std; HINTERNET hOpen, hFile; char buffer[200]; DWORD ret; int main() { hOpen = InternetOpen("Mozilla/5.0", INTERNET_OPEN_TYPE_PRECONFIG, NULL, NULL, 0); if (!hOpen) { cout << "error: no connection" << endl; return 0; } hFile = InternetOpenUrl(hOpen, "", NULL, 0, 0, 0); if (!hFile) { cout << "error: 'check website' offline" << endl; return 0; } InternetReadFile(hFile, buffer, sizeof(buffer), &ret); cout << buffer; return 0; }
Thx in advance | https://www.daniweb.com/programming/software-development/threads/161153/parsing-a-char | CC-MAIN-2017-09 | refinedweb | 185 | 68.36 |
Creating a REST API Interface
Our REST API Interface
We will be making HTTP Calls to our server via our HTTP Client. That HTTP Client is Retrofit in this case. Retrofit is the perfect fit for our project because it’s both fast, convenient to use and well documented. It’s convenient since it saves us from having to manually parse our JSON data when we download it, or encode our Form data to be sent to the server.
Through Retrofit, we only need to:
- Create an interface to map to our API methods.
- Instantiate Retrofit.
- Enqueue a Call.
In this lesson we will do the first: creating an interface with methods that map to our server side API methods.
The second part, the instantiation of retrofit, occurs in the Utils class while the last part, the enqueing of our Calls will take place in our
ScientistsActivity class and the
CRUDActivity class.
Let’s start.
Video Tutorial(Recommended)
First create a java file called
RestApi.java.
Then add our imports:
import retrofit2.Call; import retrofit2.http.Field; import retrofit2.http.FormUrlEncoded; import retrofit2.http.GET; import retrofit2.http.POST;
Then define our interfce:
public interface RestApi {
(a). Making a HTTP GET Request
Let’s start by defining our first API method. Add it inside the interface:
@GET("index.php") Call<ResponseModel> retrieve();
You can see above we’ve defined an abstract method called
retrieve(). The method doesn’t take any parameters. It instead returns a
retrofit2.Call object of generic parameter
ResponseModel. It is also decorated with the
@GET attribute. We specify the target URL in that attribute. In this case we’ve defined
index.php, which is a just a path. Remember we had defined the base part of the URL in the
Utils class.
THe above method will make a HTTP call to the server and download all our scientists.
(b). Inserting Data
Go ahead and add the following:
@FormUrlEncoded @POST("index.php") Call<ResponseModel> insertData(@Field("action") String action, @Field("name") String name, @Field("description") String description, @Field("galaxy") String galaxy, @Field("star") String star, @Field("dob") String dob, @Field("died") String died);
Above we’ve defined a method called
insertData(). That method is taking several parameters include one we’ve called
action. The above parameters, apart from the
action will be inserted into our mysql database. The action is just a string to identify our action, like in this case we are telling our server that this HTTP POST request is supposed to insert data to the database.
Again the response will be mapped to the
ResponseModel class. Note that the method is actually returning a a
retrofit2.Call object which will then be enqueued for us to asynchronously receieve a response.
You can also see that we have supplied two attributes:
@FormUrlEncoded and
@POST. In short we will be encoding our fields then making a HTTP POST request to the server.
(c). Updating Data
Now add the following method:
@FormUrlEncoded @POST("index.php") Call<ResponseModel> updateData(@Field("action") String action, @Field("id") String id, @Field("name") String name, @Field("description") String description, @Field("galaxy") String galaxy, @Field("star") String star, @Field("dob") String dob, @Field("died") String died);
Again we are making a HTTP POST request. We’ve again decorated our method with the
@FormUrlEncoded and
@POST attributes. And again we will be receiving a response of type
ResponseModel.The method is actually returning a
Call object. The action in the parameters will identify this method’s action to the server. The
id will specify the row we want to update.
(d). Searching MySQL Data
Now add the following code:
@FormUrlEncoded @POST("index.php") Call<ResponseModel> search(@Field("action") String action, @Field("query") String query, @Field("start") String start, @Field("limit") String limit);
Again we are making a HTTP POST request. This time our intention is to search data.The action parameter will specify that intention. The
query will specify our search term. Our search filter will be supporting pagination. The
start parameter will hence define our offset while the
limit will specify the number of rows to be returned.
(e). Deleting Data
Lastly add the following:
@FormUrlEncoded @POST("index.php") Call<ResponseModel> remove(@Field("action") String action, @Field("id") String id); }
The above method will allow us delete our data from our mysql database. We onlu need to specify the action as well as the id. The id will identify the row we intend to remove.
Full Code
Here’s the full code: | https://camposha.info/course/android-mysql-retrofit-full-course-insert-select-update-delete-search-pagination/lesson/creating-a-rest-api-interface/ | CC-MAIN-2019-39 | refinedweb | 749 | 59.09 |
20 January 2012 05:52 [Source: ICIS news]
By ?xml:namespace>
SINGAPORE
Prices of some petrochemical products in the region have either been falling or trading sideways since the start of the year, as demand traditionally weakens in the weeks leading to the Lunar New Year celebration, which is happening a bit early in 2012.
Some propylene sellers in northeast
An expected tightness in regional supply because of a slew of cracker turnarounds due in March should also give propylene prices a further boost, market sources said.
Offers were scant this week as some traders prefer to suspend discussions until after the Lunar New Year holiday.
Spot propylene prices were quoted at $1,350-1,400/tonne (€1,040-1,078/tonne) CFR (cost and freight) NE (northeast) Asia at midday on Friday, while naphtha values were at $960.50-962.50/tonne CFR Japan.
A South Korean producer said it had received a bid at $1,350/tonne FOB
“Cargoes are limited in the market and prices are getting better so we want to wait until after the Chinese New Year,” the producer said.
In the purified terephthalic acid (PTA) market, some sellers have taken a similar stance on transactions.
“I don't plan to sell more cargoes before holiday, as prices will rise further amid firmer energy futures and peak buying after the holiday,” a PTA trader said.
Expectations that
The upbeat sentiment that the domestic credit crunch in the world’s second biggest economy will ease was reflected in trades at the linear low density polyethylene (LLDPE) futures market at the Dalian Commodities Exchange this week.
The Chinese authorities are widely expected to adjust down the reserve requirement ratio for banks after
With external demand unlikely to pick up anytime soon as Europe struggles under the debt of its massive debt and the
In
Expectations within the country’s petrochemical market is equally upbeat on spot prices, with the upward push likely to come from tight supply since most plants in China will be shut for a full week.
Prices of styrene monomer (SM), methanol, acrylonitrile (ACN), dioctyl phthalate (DOP), urea, bisphenol-A (BPA) in the Chinese market look set to move up on restocking after the holidays, market sources said.
In some products, demand may not rebound as strongly as can be hoped, but high feedstock costs will push prices higher.
“Everything is so uncertain and we are not sure whether demand for synthetic rubber will rebound after the Lunar New Year,” a Chinese synthetic rubber producer said. Synthetic rubber producers in
Soaring feedstock BD costs have climbed to $3,100/tonne CFR (cost and freight) northeast (NE) Asia and have eroded the margins of synthetic rubber producers in
However, the downstream tyre producers are also feeling the squeeze from falling tyre export sales.
A number of small and mid-sized tyre producers in
“The small and mid-sized tyre producers in
In the Asian ammonia market, players are hoping the uptick in demand seen in January will continue to help prices stabilise after the holidays.
Spot ammonia prices have been on a downward trend since December given a reduction in demand from downstream applications such as acrylonitrile and caprolactam.
"Ammonia demand from the chemicals sector has been improving, as plants are restarting or being run at higher rates than late last year. But I hear that ammonia demand from the fertilizers segment has not recovered yet,” said a Taiwanese buyer.
In
"Ammonia consumption is better in
Additional reporting by Peh Soo Hwee, Judith Wang, Helen Yan, Gabriela Wheeler, Natalie Hui, Jessica Mao, Nicole Zhang, Phoebe Lu, Sherry Su, Ivy Ruan, Lily Zhang, and Sam Liang
($1 = €0 | http://www.icis.com/Articles/2012/01/20/9525531/asia-petrochemical-demand-prices-to-firm-post-lunar-new.html | CC-MAIN-2014-52 | refinedweb | 612 | 50.09 |
Type: Posts; User: RedBully
Load your xml into an XmlDocument and the use an xpath query to extract it.
Read about xpath here:
Read about XmlDocument here...
Hello,
One starting point is to have 'Groups' and make your users members of those groups. Assign the permissions to the groups and infer user permission from their group membership.
You could...
A couple of things.
Your MyDocuments starts it life being null and so the call to Add will create an error becuase MyDocuments is not initialised.
Also, I do believe that XmlSerialisation...
Hello,
Google maps do have an api:
I've used it before with ASP.NET using javascript. Once you've learnt the basics of their API, it's very easy to...
This might help:
Could you extract the data from the existing classes and put it into your own class. You could then serialise your own class.
If you want to use the XmlSerialiser, remember that only public...
One of the first things to try in IE8 is to turn on compatibility view. I found that even some asp.net web controls just don't work unless compatibility view is turned on.
I like your solution.
Using a single instance of a non static class that you share between your objects (as you have done) can be a better way because:
1. Having global objects means that...
Your public class is not static and so therefore not really 'Global' in the way you want it to be. You will need to make your member variable static too. You would access it using...
Glad I could be of help! :) Please mark this thread as resolved.
Here is some sample code that works and should give you an idea of how to acheive what you want.
We have an Aspx page with a menu called MainMenu. We set two styles on it for menu items and...
firstClassFullyOccupied &= SeatList[i, j];
is the same as writing
firstClassFullyOccupied = firstClassFullyOccupied & SeatList[i, j];
Please see...
In your call to UploadFileAsync, add an extra parameter (object userToken) that is the ip address or some other unique identifier.
wc.UploadFileAsync(new Uri("http://" + _ip + DBPath), "POST",...
Always need to be careful with type conversion.
This code works here:
decimal numbers = 1863.8M;
int percentage = 20;
decimal result = 0.0M;
result = numbers / percentage *...
Your break statement is breaking out of the inner for loop and not the outer for loop. This means you are still checking seats in first class even though you have found that there is a free seat. As...
Sounds like an interesting project. Must give that a try sometime.
This article may help:
I ran your program and closed both 64bit and 32bit Internet Explorer. I'm running 64bit Windows 7.
Let me know how it goes.
I prefer to you use List<myClass> instead of myClass[] because list has the Sort method on it.
List<myClass> instances = new List<myClass>();
instances.Add(new...
You need to inherit from IComparer or IComparer<myClass>
e.g.
public class myClass : IComparable<myClass>
{
int[] ints1;
int[] ints2;
Excellent. That's good news. Please mark this thread as 'Resolved'
This is what I came up with but I'm unhappy with all the conversions going on
const int GEN_SIZE = 5;
string text = setpointBoxQS.Text;
byte[] gen = new...
This should work for 32bit programs too. It looks like you're navigating to the executable in your file system.
32 bit apps on a 64bit OS are normally stored in C:\Program Files (x86) instead of...
I think first port of call is to be able to read in the PST files for which you'll need to know the format:
You can then...
Each class has an array of ints in it
e.g. myClass 1 could have an ints2 array of 1,2,3,4,5
e.g. myClass 2 could have an ints2 array of 1,2,3,4,5
In this case, when you sort your array of...
All the data you need is in the countyCount dictionary.
Put a break point in the final foreach loop I wrote and you'll see that the name variable will step through the names our your counties and... | http://forums.codeguru.com/search.php?s=036e9506755bb0db77ebf698faecc577&searchid=8423291 | CC-MAIN-2016-07 | refinedweb | 701 | 76.62 |
exec(2) exec(2)
NAME
execl(), execle(), execlp(), execv(), execve(), execvp() - execute a
file
SYNOPSIS
#include <<<<unistd.h>>>>
extern char **environ;
int execl(const char *path,
const char *arg0, ...
/*
* [const char *arg1, ..., const char *argn,]
*/
(char *)0
);
int execle(const char *path,
const char *arg0, ...
/*
* [const char *arg1, ..., const char *argn,]
*/
(char *)0,
char * const envp[]
);
int execlp(const char *file,
const char *arg0, ...
/*
* [const char *arg1, ..., const char *argn,]
*/
(char *)0
);
int execv(const char *path, char * const argv[]);
int execve(const char *path, char * const argv[], char * const envp[]);
int execvp(const char *file, char * const argv[]);
Remarks
The ANSI C ", ..." construct denotes a variable length argument list
whose optional and required members are given in the associated comment
(/* */).
DESCRIPTION
The exec*() system calls, in all their forms, load a program from an
ordinary, executable file into the current process, replacing the
current program. The path or file argument refers to either an
executable object file or a file of data for an interpreter. In the
latter case, the file of data is also called a script file.
Hewlett-Packard Company - 1 - HP-UX Release 11i: November 2000
exec(2) exec(2) exec function fails and returns to the caller, threads
and light weight processes (LWPs) in the calling process will not be
terminated.
An executable object file consists of a header (see a.out(4)), text
segment, and data segment. The data segment contains an initialized
portion and an uninitialized portion (bss). For execlp() and execvp()
the POSIX shell (see sh-posix(1)) can be loaded to interpret a script
instead. A successful call to exec*() does not return because the new
program overwrites the calling program.
When a C program is executed, it is called as follows:
main (int argc, char **argv, char **envp)
containing the new program.
file (in execlp() or execvp()) points to a file name identifying the
executable file containing the new program. The path prefix for this
file is obtained by searching the directories passed in the
environment variable PATH (see environ
program. execle() and
execve(), the C run-time start-off routine places a pointer to the
Hewlett-Packard Company - 2 - HP-UX Release 11i: November 2000
exec(2) exec(2)
environment of the calling program in the global cell:
extern char **environ;
and it is used to pass the environment of the calling program to the
new program.
Multi-threaded applications should not use the environ variable to
access or modify any environment variable while another thread is
concurrently exec*(),
except that signals caught by the process are set to their default
values (see signal(2)).
If the set-user-ID mode bit of the executable file pointed to by path
or file is set (see chmod(2)), exec*(). Note
that the set-user-ID and set-group-ID functions do not apply to
scripts; thus, if execlp() or execvp() executes a script, the set-
user-ID and set-group-ID bits are ignored, even if they are set.
The saved user ID and saved group ID of the process are always set to
the effective user ID and effective group ID, respectively, of the
process at the end of the exec*(),:
Hewlett-Packard Company - 3 - HP-UX Release 11i: November 2000
exec(2) exec(2)
+ current working directory
+ file creation mode mask (see umask(2))
+ file locks (see fcntl(2)), except for files closed-on-
execution
+ file size limit (see ulimit(2))
+ interval timers (see getitimer(2))
+ nice value (see nice(2))
+ nice value (see parent process ID)
+ pending signals
+ process ID
+ process group ID
+ real user ID
+ real group ID
+ process start time
+ real-time priority (see rtprio(2))
+ root directory (see chroot(2))
+ semadj values (see semop(2))
+ session membership
+ signal mask (see sigvector(2))
+ supplementary group IDs
+ time left until an alarm clock signal (see alarm(2))
+ trace flag (see the PT_SETTRC request of ptrace(2))
+ tms_utime, tms_stime, tms_cutime, and tms_cstime (see
times(2))
For a script file, the initial line of a script file must begin with
#! as the first two bytes, followed by zero or more spaces, followed
by interpreter or interpreter argument, as in:
#! interpreter [argument]
One or more spaces or tabs must separate interpreter and argument.
The first line should end with either a newline or a null character.
When the script file is executed, the system executes the specified
interpreter as an executable object file. Even in the case of
execlp() or execvp(), no path searching is done of the interpreter
name.
The argument is anything that follows interpreter and tabs or spaces.
If an argument is given, it is passed to the interpreter as argv[1],
and the name of the script file is passed as argv[2]. Otherwise, the
name of the script file is passed as argv[1]. argv[0] is passed as
specified in the exec*() call. All other arguments specified in the
exec*() call are passed following the name of the script file (that
is, beginning at argv[3] if there is an argument; otherwise, at
argv[2]).
Some interpreters process the interpreter and the argument internally,
and do not provide the interpreter and the argument to the users
script.
Hewlett-Packard Company - 4 - HP-UX Release 11i: November 2000
exec(2) exec(2)
If the initial line of the script file exceeds a system-defined
maximum number of characters, exec*() fails. The minimum value for
this limit is 32.
The set-user-ID and set-group-ID bits are honored for the script but
not for the interpreter.
For a executable object file, the arguments are passed as argv[1],
..., argv[n]. argv[0] is passed as specified in the exec*() call,
unless either argv or argv[0] is null as specified, in which case a
pointer to a null string is passed as argv[0].
RETURN VALUE
If exec*() returns to the calling program, an error has occurred; the
return value is -1 and errno is set to indicate the error.
ERRORS
If exec*() fails and returns to the calling program, errno is set to
one of the following values:
[E2BIG] The number of bytes in the new program's
argument list plus environment is greater
than the system-imposed limit. This limit is
at least 5120 bytes on HP-UX systems.
[EACCES] Read permission is denied for the executable
file or interpreter, and the trace flag (see
ptrace(2) request PT_SETTRC) of the process
is set.
[EACCES] Search permission is denied for a directory
listed in the executable file's or the
interpreter's path prefix.
[EACCES] The executable file or the interpreter is not
an ordinary file.
[EACCES] The file described by path or file is not
executable. The superuser cannot execute a
file unless at least one access permission
bit or entry in its access control list has
an execute bit set.
[EFAULT] path, argv, or envp point to an illegal
address. The reliable detection of this
error is implementation dependent.
[EINTR] A signal was caught during the exec*() system
call.
Hewlett-Packard Company - 5 - HP-UX Release 11i: November 2000
exec(2) exec(2)
[EINVAL] The executable file is incompatible with the
architecture on which the exec*() has been
performed, and is presumed to be for a
different architecture. It is not guaranteed
that every architecture's executable files
will be recognized.
[ELOOP] Too many symbolic links were encountered in
translating the path name.
[ENAMETOOLONG] The executable file's path name or the
interpreter's path name exceeds PATH_MAX
bytes, or the length of a component of the
path name exceeds NAME_MAX bytes while
_POSIX_NO_TRUNC is in effect.
[ENOENT] path is null.
[ENOENT] One or more components of the executable
file's path name or the interpreter's path
name does not exist.
[ENOEXEC] The executable file is shorter than indicated
by the size values in its header, or is
otherwise inconsistent. The reliable
detection of this error is implementation
dependent.
[ENOEXEC] The function call is not execlp() or
execvp(), and the executable file has the
appropriate access permission, but there is
neither a valid magic number nor the
characters #! as the first two bytes of the
file's initial line.
[ENOEXEC] The number of bytes in the initial line of a
script file exceeds the system's maximum.
[ENOMEM] The new process requires more memory than is
available or allowed by the system-imposed
maximum.
[ENOTDIR] A component of the executable file's path
prefix or the interpreter's path prefix is
not a directory.
[ETXTBSY] The executable file is currently open for
writing.
WARNINGS
Hewlett-Packard Company - 6 - HP-UX Release 11i: November 2000
exec(2) exec(2)
Unsharable executable files are not supported. These are files whose
EXEC_MAGIC magic number was produced with the -N option of ld (see
ld(1)).
It is recommended to use the execve() call in multi-threaded
applications to avoid possible deadlocks.
DEPENDENCIES
HP Process Resource Manager
If the optional HP Process Resource Manager (PRM) software is
installed and configured, the process's process resource group ID is
not changed by exec*(). See prmconfig(1) for a description of how to
configure HP PRM, and prmconf(4) for the definition of process
resource group.
SEE ALSO
sh(1), sh-posix(1), alarm(2), exit(2), fork(2), nice(2), ptrace(2),
semop(2), signal(2), times(2), ulimit(2), umask(2), a.out(4), acl(5),
environ(5), signal(5).
HP Process Resource Manager: prmconfig(1), prmconf(4) in HP Process
Resource Manager User's Guide.
STANDARDS CONFORMANCE
environ: AES, SVID2, SVID3, XPG2, XPG3, XPG4, FIPS 151-2, POSIX.1
execl(): AES, SVID2, SVID3, XPG2, XPG3, XPG4, FIPS 151-2, POSIX.1
execle(): AES, SVID2, SVID3, XPG2, XPG3, XPG4, FIPS 151-2, POSIX.1
execlp(): AES, SVID2, SVID3, XPG2, XPG3, XPG4, FIPS 151-2, POSIX.1
execv(): AES, SVID2, SVID3, XPG2, XPG3, XPG4, FIPS 151-2, POSIX.1
execve(): AES, SVID2, SVID3, XPG2, XPG3, XPG4, FIPS 151-2, POSIX.1
execvp(): AES, SVID2, SVID3, XPG2, XPG3, XPG4, FIPS 151-2, POSIX.1
Hewlett-Packard Company - 7 - HP-UX Release 11i: November 2000 | http://modman.unixdev.net/?sektion=2&page=execve&manpath=HP-UX-11.11 | CC-MAIN-2017-17 | refinedweb | 1,680 | 61.06 |
In machine learning, the difference between the predicted output and the actual output is used to tune the parameters of the algorithm. This error in prediction, so called loss, is a crucial part of designing a good model as it evaluates the performance of our model. For accurate predictions, one needs to minimize this loss. In neural networks, it is done using the gradient descent. There are many types loss functions. Some of them are:
Mean squared error is the most common used loss function for regression loss. It minimizes the squared difference between the predicted value and the actual value. The residual sum of squares is defined as:
import numpy as np def l2_loss(yhat, y): return np.sum((yhat - y)**2))
L1 loss minimized the sum of absolute error between the predicted value and the actual value.
def l1_loss(yhat, y): return np.sum(np.absolute(yhat - y))
Note: L1 and L2 are also used in regularization. Don’t get confused.
The hinge loss is used for classification problems e.g. in case of suppport vector machines. It is defined as:
def hinge(yhat, y): return np.max(0, 1 - yhat * y)
The cross-entropy loss is also used in case of classification problems for estimating the accuracy of model whose output is a probability,
p, which lies between 0 and 1. In case of binary classification, it can be written as:
For multi-class classification problems, it is:
Here,
y is a binary indicator (0 or 1) if class label
c is the correct classification for observation
o and
p is predicted probability observation s.t.
o is of class
c.
def cross_entropy(y, p): return -np.sum(np.multiply(y, np.log(p)) + np.multiply((1-y), np.log(1-p)))
For a detailed example using log loss, check logistic regression implementation on GitHub: kHarshit/ML-py.
The choice of loss function depends on the class of problem (regression / classification) as well as is sometimes specific to the problem.
References: | https://kharshit.github.io/blog/2018/08/24/loss-functions | CC-MAIN-2020-16 | refinedweb | 334 | 56.86 |
This manual is for GNU libmicrohttpd (version 0.9.39, 22 December 2014), a library for embedding an HTTP(S) server into C".
All symbols defined in the public API start with
MHD_. MHD
is a small HTTP daemon library. As such, it does not have any API
for logging errors (you can only enable or disable logging to stderr).
Also, it may not support all of the HTTP features directly, where
applicable, portions of HTTP may have to be handled by clients of the
library.
The library is supposed to handle everything that it must handle
(because the API would not allow clients to do this), such as basic
connection management; however, detailed interpretations of headers —
such as range requests — and HTTP methods are left to clients. The
library does understand
HEAD and will only send the headers of
the response and not the body, even if the client supplied a body. The
library also understands headers that control connection management
(specifically,
Connection: close and
Expect: 100 continue
are understood and handled automatically).
MHD understands
POST data and is able to decode certain
formats (at the moment only
application/x-www-form-urlencoded
and
multipart/form-data) using the post processor API. The
data stream of a POST is also provided directly to the main
application, so unsupported encodings could still be processed, just
not conveniently by MHD.
The header file defines various constants used by the HTTP protocol. This does not mean that MHD actually interprets all of these values. The provided constants are exported as a convenience for users of the library. MHD does not verify that transmitted HTTP headers are part of the standard specification; users of the library are free to define their own extensions of the HTTP standard and use those with MHD.
All functions are guaranteed to be completely reentrant and thread-safe. MHD checks for allocation failures and tries to recover gracefully (for example, by closing the connection). Additionally, clients can specify resource limits on the overall number of connections, number of connections per IP address and memory used per connection to avoid resource exhaustion.
MHD is currently used in a wide range of implementations. Examples based on reports we’ve received from developers include:
MHD supports four basic thread modes and up to three event loop styes.
The four basic thread modes are external (MHD creates no threads, event loop is fully managed by the application), internal (MHD creates one thread for all connections), thread pool (MHD creates a thread pool which is used to process all connections) and thread-per-connection (MHD creates one listen thread and then one thread per accepted connection).
These thread modes are then combined with the event loop styles. MHD support select, poll and epoll. epoll is only available on Linux, poll may not be available on some platforms. Note that it is possible to combine MHD using epoll with an external select-based event loop.
The default (if no other option is passed) is “external select”.
The highest performance can typically be obtained with a thread pool
using
epoll. Apache Benchmark (ab) was used to compare the
performance of
select and
epoll when using a thread pool
and a large number of connections. fig:performance shows the
resulting plot from the
benchmark.c example, which measures the
latency between an incoming request and the completion of the
transmission of the response. In this setting, the
epoll
thread pool with four threads was able to handle more than 45,000
connections per second on loopback (with Apache Benchmark running
three processes on the same machine).
Figure 1.1: Performance measurements for select vs. epoll (with thread-pool).
Not all combinations of thread modes and event loop styles are
supported. This is partially to keep the API simple, and partially
because some combinations simply make no sense as others are strictly
superior. Note that the choice of style depends fist of all on the
application logic, and then on the performance requirements.
Applications that perform a blocking operation while handling a
request within the callbacks from MHD must use a thread per
connection. This is typically rather costly. Applications that do
not support threads or that must run on embedded devices without
thread-support must use the external mode. Using
epoll is only
supported on Linux, thus portable applications must at least have a
fallback option available. tbl:supported lists the sane
combinations.
Table 1.1: Supported combinations of event styles and thread modes.
MHD uses the standard GNU system where the usual build process involves running
$ ./configure $ make $ make install
MHD supports various options to be given to configure to tailor the binary to a specific situation. Note that some of these options will remove portions of the MHD code that are required for binary-compatibility. They should only be used on embedded systems with tight resource constraints and no concerns about library versioning. Standard distributions including MHD are expected to always ship with all features enabled, otherwise unexpected incompatibilities can arise!
Here is a list of MHD-specific options that can be given to configure (canonical configure options such as “–prefix” are also supported, for a full list of options run “./configure –help”):
``--disable-curl''
disable running testcases using libcurl
``--disable-largefile''
disable support for 64-bit files
``--disable-messages''
disable logging of error messages (smaller binary size, not so much fun for debugging)
``--disable-https''
disable HTTPS support, even if GNUtls is found; this option must be used if eCOS license is desired as an option (in all cases the resulting binary falls under a GNU LGPL-only license)
``--disable-postprocessor''
do not include the post processor API (results in binary incompatibility)
``--disable-dauth''
do not include the authentication APIs (results in binary incompatibility)
``--disable-epoll
do not include epoll support, even on Linux (minimally smaller binary size, good for testing portability to non-Linux systems)
``--enable-coverage''
set flags for analysis of code-coverage with gcc/gcov (results in slow, large binaries)
``--with-gcrypt=PATH''
specifies path to libgcrypt installation
``--with-gnutls=PATH''
specifies path to libgnutls installation
Ideally, before including "microhttpd.h" you should add the necessary
includes to define the
uint64_t,
size_t,
fd_set,
socklen_t and
struct sockaddr data types. Which
specific headers are needed may depend on your platform and your build
system might include some tests to provide you with the necessary
conditional operations. For possible suggestions consult
platform.h and
configure.ac in the MHD distribution.
Once you have ensured that you manually (!) included the right headers
for your platform before "microhttpd.h", you should also add a line
with
#define MHD_PLATFORM_H which will prevent the
"microhttpd.h" header from trying (and, depending on your platform,
failing) to include the right headers.
If you do not define MHD_PLATFORM_H, the "microhttpd.h" header will automatically include headers needed on GNU/Linux systems (possibly causing problems when porting to other platforms).
MHD does not install a signal handler for SIGPIPE. On platforms where this is possible (such as GNU/Linux), it disables SIGPIPE for its I/O operations (by passing MSG_NOSIGNAL). On other platforms, SIGPIPE signals may be generated from network operations by MHD and will cause the process to die unless the developer explicitly installs a signal handler for SIGPIPE.
Hence portable code using MHD must install a SIGPIPE handler or
explicitly block the SIGPIPE signal. MHD does not do so in order
to avoid messing with other parts of the application that may
need to handle SIGPIPE in a particular way. You can make your application handle SIGPIPE by calling the following function in
main:
static void catcher (int sig) { } static void ignore_sigpipe () { struct sigaction oldsig; struct sigaction sig; sig.sa_handler = &catcher; sigemptyset (&sig.sa_mask); #ifdef SA_INTERRUPT sig.sa_flags = SA_INTERRUPT; /* SunOS */ #else sig.sa_flags = SA_RESTART; #endif if (0 != sigaction (SIGPIPE, &sig, &oldsig)) fprintf (stderr, "Failed to install SIGPIPE handler: %s\n", strerror (errno)); }
Some platforms do not support
long long. Hence MHD defines a
macro
MHD_UNSIGNED LONG_LONG which will default to
unsigned long long. For standard desktop operating systems,
this is all you need to know.
However, if your platform does not support
unsigned long long,
you should change "platform.h" to define
MHD_LONG_LONG and
MHD_UNSIGNED_LONG_LONG to an appropriate alternative type and
also define
MHD_LONG_LONG_PRINTF and
MHD_UNSIGNED_LONG_LONG_PRINTF to the corresponding format
string for printing such a data type. Note that the “signed”
versions are deprecated. Also, for historical reasons,
MHD_LONG_LONG_PRINTF is without the percent sign, whereas
MHD_UNSIGNED_LONG_LONG_PRINTF is with the percent sign. Newly
written code should only use the unsigned versions. However, you need
to define both in "platform.h" if you need to change the definition
for the specific platform.
libmicrohttpd in general ported well to W32. Most libmicrohttpd features are supported. W32 do not support some functions, like epoll and corresponding MHD features are not available on W32.
To compile MHD on z/OS, extract the archive and run
iconv -f UTF-8 -t IBM-1047 contrib/ascebc > /tmp/ascebc.sh chmod +x /tmp/ascebc.sh for n in `find * -type f` do /tmp/ascebc.sh $n done
to convert all source files to EBCDIC. Note that you must run
configure from the directory where the configure script is
located. Otherwise, configure will fail to find the
contrib/xcc script (which is a wrapper around the z/OS c89
compiler).
Options for the MHD daemon.
Note that if neither
MHD_USE_THREAD_PER_CONNECTION nor
MHD_USE_SELECT_INTERNALLY flag set.
MHD_USE_SSL
Run in HTTPS-mode. If you specify
MHD_USE_SSL and MHD was
compiled without SSL support,
MHD_start_daemon will and the local platform does not
support it,
MHD_start_daemon will return NULL.
If you want MHD to support IPv4 and IPv6 using a single socket, pass MHD_USE_DUAL_STACK, otherwise, if you only pass this option, MHD will try to bind to IPv6-only (resulting in no IPv4 support).
MHD_USE_DUAL_STACK
Use a single socket for IPv4 and IPv6. Note that this will mean that IPv4 addresses are returned by MHD in the IPv6-mapped format (the ’struct sockaddr_in6’ format will be used for IPv4 and IPv6).
MHD_USE_PEDANTIC_CHECKS
Be pedantic about the protocol (as opposed to as tolerant as possible).
Specifically, at the moment, this flag causes MHD to reject HTTP
1.1 connections without a
Host header. currently only works in conjunction
with
MHD_USE_THREAD_PER_CONNECTION or
MHD_USE_INTERNAL_SELECT (at this point). If you specify
MHD_USE_POLL and the local platform does not support it,
MHD_start_daemon will return NULL.
MHD_USE_EPOLL_LINUX_ONLY
Use epoll instead of poll or select. This allows sockets with
descriptors
>= FD_SETSIZE. This option is only available on
Linux systems and only works in conjunction with
MHD_USE_THREAD_PER_CONNECTION (at this point). If you specify
MHD_USE_EPOLL_LINUX_ONLY and the local platform does not
support it,
MHD_start_daemon will return NULL. Using epoll
instead of select or poll can in some situations result in significantly
higher performance as the system call has fundamentally lower complexity
(O(1) for epoll vs. O(n) for select/poll where n is the number of
open connections). is going to be used exclusively to
connect HTTP clients to the HTTP server. This option is incompatible
with using a thread pool; if it is used,
MHD_OPTION_THREAD_POOL_SIZE is ignored.
MHD_USE_PIPE_FOR_SHUTDOWN
Force MHD to use a signal pipe to notify the event loop (of threads)
of our shutdown. This is required if an appliction uses
MHD_USE_INTERNAL_SELECT or
MHD_USE_THREAD_PER_CONNECTION
and then performs
MHD_quiesce_daemon (which eliminates our
ability to signal termination via the listen socket). In these modes,
MHD_quiesce_daemon will fail if this option was not set. Also,
use of this option is automatic (as in, you do not even have to
specify it), if
MHD_USE_NO_LISTEN_SOCKET is specified. In
"external" select mode, this option is always simply ignored.
MHD_USE_SUSPEND_RESUME
Enables using
MHD_suspend_connection and
MHD_resume_connection, as performing these calls requires some
additional pipes to be created, and code not using these calls should
not pay the cost.
MHD_USE_TCP_FASTOPEN
Enable TCP_FASTOPEN on the listen socket. TCP_FASTOPEN is currently
supported on Linux >= 3.6. On other systems using this option with
cause
MHD_start_daemon to fail.. Values above 128k are unlikely to
result in much benefit, as half of the memory will be typically used
for IO, and TCP buffers are unlikely to support window sizes above 64k
on most systems.
MHD_OPTION_CONNECTION_MEMORY_INCREMENT
Increment to use for growing the read buffer (followed by a
size_t). The default is 1024 (bytes). Increasing this value
will make MHD use memory for reading more aggressively, which can
reduce the number of
recvfrom calls but may increase the number
of
sendto calls. The given value must fit within
MHD_OPTION_CONNECTION_MEMORY_LIMIT.
MHD_OPTION_CONNECTION_LIMIT
Maximum number of concurrent connections to accept (followed by an
unsigned int). The default is
FD_SETSIZE - 4 (the
maximum number of file descriptors supported by
select minus
four for
stdin,
stdout,
stderr and
where the return value will be passed as
*con_cls in calls to the
MHD_AccessHandlerCallback
when this request is processed later; returning a
value of
NULL has no special significance; (however,
note that if you return non-
NULL, you can no longer
rely on the first call to the access handler having
NULL == *con_cls on entry)
cls will be set to the second argument following
MHD_OPTION_URI_LOG_CALLBACK. Finally,
uri will
be the 0-terminated URI of the request.
Note that during the time of this call, most of the connection’s state is not initialized (as we have not yet parsed he headers). However, information about the connecting client (IP, socket) is available._HTTPS_CERT_CALLBACK
Use a callback to determine which X.509 certificate should be used for a given HTTPS connection. This option should be followed by a argument of type "gnutls_certificate_retrieve_function2 *". This option provides an alternative to MHD_OPTION_HTTPS_MEM_KEY and MHD_OPTION_HTTPS_MEM_CERT. You must use this version if multiple domains are to be hosted at the same IP address using TLS’s Server Name Indication (SNI) extension. In this case, the callback is expected to select the correct certificate based on the SNI information provided. The callback is expected to access the SNI data using gnutls_server_name_get(). Using this option requires GnuTLS 3.0 or higher. returns
NULL for:
For options that expect a single pointer argument, the
second member of the
struct MHD_OptionItem form
where the return value must be
strlen(s) and
s should be
updated. Note that the unescape function must not lengthen
s
(the result must be shorter than the input and still be 0-terminated).
cls).
MHD_OPTION_TCP_FASTQUEUE_QUEUE_SIZE
When the flag
MHD_USE_TCP_FASTOPEN is used, this option sets the
connection handshake queue size for the TCP FASTOPEN connections. Note
that a TCP FASTOPEN connection handshake occupies more resources than a
TCP handshake as the SYN packets also contain DATA which is kept in the
associate state until handshake is completed. If this option is not
given the queue size is set to a default value of 10. This option must
be followed by a
unsigned int.
MHD_OPTION_HTTPS_MEM_DHPARAMS
Memory pointer for the Diffie-Hellman parameters (dh.pem) to be used
by the HTTPS daemon for key exchange. This option must be followed by
a
const char * argument. The argument would be a zero-terminated
string with a PEM encoded PKCS3 DH parameters structure suitable
for passing to
gnutls_dh_parms_import_pkcs3.
MHD_OPTION_LISTENING_ADDRESS_REUSE
This option must be followed by a
unsigned int argument.
If this option is present and true (nonzero) parameter is given, allow reusing
the address:port of the listening socket (using
SO_REUSEPORT on most
platforms, and
SO_REUSEADDR on Windows). If a false (zero) parameter is
given, disallow reusing the the address:port of the listening socket (this
usually requires no special action, but
SO_EXCLUSIVEADDRUSE is needed on
Windows). If this option is not present, default behaviour is undefined
(currently,
SO_REUSEADDR is used on all platforms, which disallows
address:port reusing with the exception of Windows).
Entry in an MHD_OPTION_ARRAY. See the
MHD_OPTION_ARRAY option
argument for its use.
The
option member is used to specify which option is specified
in the array. The other members specify the respective argument.
Note that for options taking only a single pointer, the
ptr_value member should be set. For options taking two pointer
arguments, the first pointer must be cast to
intptr_t and both
the
value and the
ptr_value members should be used to
pass the two pointers.
The
MHD_ValueKind specifies data.Code specifiesMode specifies.
Response-specific flags. Passed as an argument to
MHD_set_response_options().
MHD_RF_NONE
No special handling.
MHD_RF_HTTP_VERSION_1_0_ONLY
Only respond in conservative HTTP 1.0-mode. In particular, do not (automatically) sent "Connection" headers and always close the connection after generating the response.
Response-specific options. Passed in the varargs portion of
MHD_set_response_options().
MHD_RO_END
No more options / last option. This is used to terminate the VARARGs list.
Handle for the daemon (listening on a socket for HTTP traffic).
Handle for a connection / HTTP request. With HTTP/1.1, multiple requests can be run over the same connection. However, MHD will only show one request per TCP connection to the client at any given time.
Handle for a response.
Handle for
POST processing.
Information about a connection.
Information about an MHD daemon..).
Adding a
POST processor,.
Set a handler for fatal errors.
function to call if MHD encounters a fatal internal error. If no handler was set explicitly, MHD will call
abort.
closure argument for cb; the other arguments are the name of the source file, line number and a string describing the nature of the fatal error (which can be
NULL)
Start a webserver on the given port.
OR-ed combination of
MHD_FLAG values;
port to bind to;
callback to call to check which clients will be allowed to connect; you
can pass
NULL in which case connections from any IP will be
accepted;
extra argument to apc;
default handler for all URIs;
extra argument to dh.
Additional arguments are a list of options (type-value pairs,
terminated with
MHD_OPTION_END). It is mandatory to use
MHD_OPTION_END as last argument, even when there are no
additional arguments.
Return
NULL on error, handle to daemon on success.
Stop accepting connections from the listening socket. Allows clients
to continue processing, but stops accepting new connections. Note
that the caller is responsible for closing the returned socket;
however, if MHD is run using threads (anything but external select
mode), it must not be closed until AFTER
MHD_stop_daemon has
been called (as it is theoretically possible that an existing thread
is still using it).
This function is useful in the special case that a listen socket is to be migrated to another process (i.e. a newer version of the HTTP server) while existing connections should continue to be processed until they are finished.
Return
-1 on error (daemon not listening), the handle to the
listen socket otherwise.
Shutdown an HTTP daemon.
Run webserver operations (without blocking unless in client callbacks).
This method should be called by clients in combination with
MHD_get_fdset() if the client-controlled
select-method is used.
This function will work for external
poll and
select mode.
However, if using external
select mode, you may want to
instead use
MHD_run_from_select, as it is more efficient.
daemon to process connections of
Return
MHD_YES on success,
MHD_NO if this daemon was not
started with the right options for this call.
Run webserver operations given sets of ready socket handles.
This method should be called by clients in combination with
MHD_get_fdset if the client-controlled (external)
select method is used.
You can use this function instead of
MHD_run if you called
select on the result from
MHD_get_fdset. File descriptors in
the sets that are not controlled by MHD will be ignored. Calling
this function instead of
MHD_run is more efficient as MHD will
not have to call
select again to determine which operations are
ready.
daemon to process connections of
set of descriptors that must be ready for reading without blocking
set of descriptors that must be ready for writing without blocking
ignored, can be NULL
Return
MHD_YES on success,
MHD_NO on serious internal
errors., or if you are building a proxy.
If you use this API in conjunction with a internal select or a thread
pool, you must set the option
MHD_USE_PIPE_FOR_SHUTDOWN to
ensure that the freshly added connection is immediately processed by
MHD.
The given client socket will be managed (and closed!) by MHD after this call and must no longer be used directly by the application afterwards.
daemon that manages the connection
socket to manage (MHD will expect to receive an HTTP request from this socket next).
IP address of the client
number of bytes in addr
This function will return
MHD_YES on success,
MHD_NO if this daemon could
not handle the connection (i.e. malloc failed, etc).
The socket will be closed in any case; ’errno’ is set
to indicate further details about the error. on success,
MHD_NO if: the arguments are
invalid (example:
NULL pointers); this daemon was not started with
the right options for this call.
Obtain timeout value for select for this daemon (only needed if
connection timeout is used). The returned value is how many
milliseconds
select should at most block, not the timeout value
set for connections. This function must not be called if the
MHD_USE_THREAD_PER_CONNECTION mode is in use (since then it is
not meaningful to ask for a timeout, after all, there is concurrenct
activity). The function must also not be called by user-code if
MHD_USE_INTERNAL_SELECT is in use. In the latter case, the
behavior is undefined.
which daemon to obtain the timeout from.
will be set to the timeout (in milliseconds).
Return
MHD_YES on success,
MHD_NO if timeouts are not used
(or no connections exist that would necessiate the use of a timeout
right now).
Get all the headers matching kind from the request.
The iterator callback is invoked once for each header, with iterator_cls as first argument. After version 0.9.19, the headers are iterated in the same order as they were received from the network; previous versions iterated over the headers in reverse order.
MHD_get_connection_values returns the number of entries
iterated over; this can be less than the number of headers if, while
iterating, iterator returns
MHD_NO.
iterator can be
NULL: in this case this function just counts
and returns the number of headers.
In the case of
MHD_GET_ARGUMENT_KIND, the value argument
will be
NULL if the URL contained a key without an equals operator.
For example, for a HTTP request to the URL “”, the
value argument is
NULL; in contrast, a HTTP request to the URL
“”, the value argument is the empty string.
The normal case is that the URL contains “”
in which case value would be the string “value” and key
would contain the string “key”.
This function can be used to append an entry to
the list of HTTP headers of a connection (so that the
MHD_get_connection_values function will return
them – and the MHD PostProcessor will also
see them). This maybe required in certain
situations (see Mantis #1399) where (broken)
HTTP implementations fail to supply values needed
by the post processor (or other parts of the
application).
This function MUST only be called from within the MHD_AccessHandlerCallback (otherwise, access maybe improperly synchronized). Furthermore, the client must guarantee that the key and value arguments are 0-terminated strings that are NOT freed until the connection is closed. (The easiest way to do this is by passing only arguments to permanently allocated strings.).
connection is the connection for which the entry for key of the given kind should be set to the given value.
The function returns
MHD_NO if the operation
could not be performed due to insufficient memory
and
MHD_YES on success.
Get a particular header value. If multiple values match the
kind, return one of them (the “first”, whatever that means).
key must reference a zero-terminated ASCII-coded string
representing the header to look for: it is compared against the
headers using
strcasecmp(), so case is ignored. A value of
NULL for key can be used to lookup ’trailing’ values without a
key, for example if a URI is of the form
“”, a key of
NULL can be used to
access “tailer" The function returns
NULL if no matching item
was found..
Queue a response to be transmitted to the client as soon as possible but only after MHD_AccessHandlerCallback returns. This function checks that it is legal to queue a response at this time for the given connection. It also increments the internal reference counter for the response object (the counter will be decremented automatically once the response has been transmitted).
the connection identifying the client;
HTTP status code (i.e.
200 for OK);
response to transmit.
Return
MHD_YES on success or if message has been queued. Return
MHD_NO: if arguments are invalid (example:
NULL pointer); on
error (i.e. reply already sent).
Destroy a response object and associated resources (decrement the reference counter). Note that MHD may keep some of the resources around if the response is still in the queue for some clients, so the memory may not necessarily be freed immediately.
An explanation of reference counting(1):
MHD_Responseobject is allocated:
MHD_Responseobject is enqueued in a
MHD_Connection:
MHD_destroy_response(): the counter’s value drops to zero and the
MHD_Responseobject is released.
Create a response object. The response object can be extended with header information and then it can be used any number of times.
size of the data portion of the response,
-1 for unknown;
preferred block size for querying crc (advisory only, MHD may still call crc using smaller chunks); this is essentially the buffer size used for IO, clients should pick a value that is appropriate for IO and memory performance requirements;
callback to use to obtain response data;
extra argument to crc;
callback to call to free crc_cls resources.
Return
NULL on error (i.e. invalid arguments, out of memory).
Create a response object. The response object can be extended with header information and then it can be used any number of times.
size of the data portion of the response (should be smaller or equal to the size of the file).
Return
NULL on error (i.e. invalid arguments, out of memory).
Create a response object. The response object can be extended with
header information and then it can be used any number of times.
Note that you need to be a bit careful about
off_t when
writing this code. Depending on your platform, MHD is likely
to have been compiled with support for 64-bit files. When you
compile your own application, you must make sure that
off_t
is also a 64-bit value. If not, your compiler may pass a 32-bit
value as
off_t, which will result in 32-bits of garbage.
If you use the autotools, use the
AC_SYS_LARGEFILE autoconf
macro and make sure to include the generated ‘config.h’ file
before ‘microhttpd.h’ to avoid problems. If you do not have a
build system and only want to run on a GNU/Linux system, you could
also use
#define _FILE_OFFSET_BITS 64 #include <sys/types.h> #include <sys/stat.h> #include <fcntl.h> #include <microhttpd.h>
to ensure 64-bit
off_t. Note that if your operating system
does not support 64-bit files, MHD will be compiled with a 32-bit
off_t (in which case the above would be wrong).
size of the data portion of the response (number of bytes to transmit from the file starting at offset)..
offset to start reading from in the file
Return
NULL on error (i.e. invalid arguments, out of memory).
Create a response object. The response object can be extended with header information and then it can be used any number of times.
size of the data portion of the response;
the data itself;
memory management options for buffer; use MHD_RESPMEM_PERSISTENT if the buffer is static/global memory, use MHD_RESPMEM_MUST_FREE if the buffer is heap-allocated and should be freed by MHD and MHD_RESPMEM_MUST_COPY if the buffer is in transient memory (i.e. on the stack) and must be copied by MHD;
Return
NULL on error (i.e. invalid arguments, out of memory).
Create a response object. The response object can be extended with
header information and then it can be used any number of times.
This function is deprecated, use
MHD_create_response_from_buffer instead.
size of the data portion of the response;
the data itself;
if true: MHD should free data when done;
if true: MHD allocates a block of memory and use it to make a copy of
data embedded in the returned
MHD_Response structure;
handling of the embedded memory is responsibility of MHD; data
can be released anytime after this call returns.
Return
NULL on error (i.e. invalid arguments, out of memory).
Example: create a response from a statically allocated string:
Add a header line to the response. The strings referenced by header and content must be zero-terminated and they are duplicated into memory blocks embedded in response.
Notice that the strings must not hold newlines, carriage returns or tab chars.
Return
MHD_NO on error (i.e. invalid header or content format or
memory allocation error).
Add a footer line to the response. The strings referenced by footer and content must be zero-terminated and they are duplicated into memory blocks embedded in response.
Notice that the strings must not hold newlines, carriage returns or tab chars. You can add response footers at any time before signalling the end of the response to MHD (not just before calling ’MHD_queue_response’). Footers are useful for adding cryptographic checksums to the reply or to signal errors encountered during data generation. This call was introduced in MHD 0.9.3.
Return
MHD_NO on error (i.e. invalid header or content format or
memory allocation error).
Delete a header (or footer) line from the response. Return
MHD_NO on error
(arguments are invalid or no such header known).
Set special flags and options for a response.
Calling this functions sets the given flags and options for the response.
which response should be modified;
flags to set for the response;
Additional arguments are a list of options (type-value pairs,
terminated with
MHD_RO_END). It is mandatory to use
MHD_RO_END as last argument, even when there are no
additional arguments.
Return
MHD_NO on error,
MHD_YES on success..
Sometimes it may be possible that clients upload data faster
than an application can process it, or that an application
needs an extended period of time to generate a response.
If
MHD_USE_THREAD_PER_CONNECTION is used, applications
can simply deal with this by performing their logic within the
thread and thus effectively blocking connection processing
by MHD. In all other modes, blocking logic must not be
placed within the callbacks invoked by MHD as this would also
block processing of other requests, as a single thread may be
responsible for tens of thousands of connections.
Instead, applications using thread modes other than
MHD_USE_THREAD_PER_CONNECTION should use the
following functions to perform flow control.
Suspend handling of network data for a given connection. This can be used to dequeue a connection from MHD’s event loop (external select, internal select or thread pool; not applicable to thread-per-connection!) for a while.
If you use this API in conjunction with a internal select or a
thread pool, you must set the option
MHD_USE_SUSPEND_RESUME to
ensure that a resumed connection is immediately processed by MHD.
Suspended connections continue to count against the total number of connections allowed (per daemon, as well as per IP, if such limits are set). Suspended connections will NOT time out; timeouts will restart when the connection handling is resumed. While a connection is suspended, MHD will not detect disconnects by the client.
The only safe time to suspend a connection is from the
MHD_AccessHandlerCallback.
Finally, it is an API violation to call
MHD_stop_daemon while
having suspended connections (this will at least create memory and
socket leaks or lead to undefined behavior). You must explicitly
resume all connections before stopping the daemon.
the connection to suspend
Resume handling of network data for suspended connection. It is safe to resume a suspended connection at any time. Calling this function on a connection that was not previously suspended will result in undefined behavior.
the connection to resume
MHD support three types of client authentication.
Basic authentication uses a simple authentication method based on BASE64 algorithm. Username and password are exchanged in clear between the client and the server, so this method must only be used for non-sensitive content or when the session is protected with https. When using basic authentication MHD will have access to the clear password, possibly allowing to create a chained authentication toward an external authentication server.
Digest authentication uses a one-way authentication method based on MD5 hash algorithm. Only the hash will transit over the network, hence protecting the user password. The nonce will prevent replay attacks. This method is appropriate for general use, especially when https is not used to encrypt the session.
Client certificate authentication uses a X.509 certificate from the client. This is the strongest authentication mechanism but it requires the use of HTTPS. Client certificate authentication can be used simultaneously with Basic or Digest Authentication in order to provide a two levels authentication (like for instance separate machine and user authentication). A code example for using client certificates is presented in the MHD tutorial.
Get the username and password from the basic authorization header sent by the client.
Return
NULL if if successful, otherwise
MHD_NO.
realm must reference to a zero-terminated string representing the realm.
response a response structure to specify what shall be presented to the client with a 401 HTTP status.
Find and return a pointer to the username value from the request header.
Return
NULL if the value is not found or header does not exist.
If returned value is not
NULL, the value must be
free()’ed.
Checks if the provided values in the WWW-Authenticate header are valid
and sound according to RFC2716. If valid return
MHD_YES, otherwise return
MHD_NO.
realm must reference to a zero-terminated string representing the realm.
username must reference to a zero-terminated string representing the username, it is usually the returned value from MHD_digest_auth_get_username.
password must reference to a zero-terminated string representing the password, most probably it will be the result of a lookup of the username against a local database.
nonce_timeout is the amount of time in seconds for a nonce to be invalid. Most of the time it is sound to specify 300 seconds as its values.
Queues a response to request authentication from the client,
return
MHD_YES if successful, otherwise
MHD_NO.
realm must reference to a zero-terminated string representing the realm.
opaque must reference to a zero-terminated string representing a value that gets passed to the client and expected to be passed again to the server as-is. This value can be a hexadecimal or base64 string.
response a response structure to specify what shall be presented to the client with a 401 HTTP status.
signal_stale a value that signals "stale=true" in the response header to
indicate the invalidity of the nonce and no need to ask for authentication
parameters and only a new nonce gets generated.
MHD_YES to generate a new
nonce,
MHD_NO to ask for authentication parameters.
Example: handling digest authentication requests and responses.:
In contrast to the previous example, for
POST requests in particular,
it is more common to use the value of
*con_cls to keep track of
actual state used during processing, such as the post processor (or a
struct containing a post processor):
Note that the callback from
MHD_OPTION_NOTIFY_COMPLETED
should be used to destroy the post processor. This cannot be
done inside of the access handler since the connection may not
always terminate normally.
POSTprocessor
Create a PostProcessor. A PostProcessor can be used to (incrementally)
parse the data portion of a
POST request.
the connection on which the
POST is happening (used to determine
the
POST format);
maximum number of bytes to use for internal buffering (used only for the parsing, specifically the parsing of the keys). A tiny value (256-1024) should be sufficient; do NOT use a value smaller than 256; for good performance, use 32k or 64k (i.e. 65536).
iterator to be called with the parsed data; must NOT be
NULL;
custom value to be used as first argument to iterator.
Return
NULL on error (out of memory, unsupported encoding), otherwise
a PP handle.
Parse and process
POST data. Call this function when
data is available (usually during an
MHD_AccessHandlerCallback)
with the upload_data and upload_data_size. Whenever
possible, this will then cause calls to the
MHD_IncrementalKeyValueIterator.
the post processor;
post_data_len bytes of
POST data;
length of post_data.
Return
MHD_YES on success,
MHD_NO on if processing completed nicely,
MHD_NO
if there were spurious characters or formatting problems with
the post request. It is common to ignore the return value
of this function.
Obtain information about the given daemon. This function is currently not fully implemented.
the daemon’). No longer supported,
using this value will cause
MHD_get_daemon_info to return NULL.
MHD_DAEMON_INFO_MAC_KEY_SIZE
Request information about the key size for a particular cipher
algorithm. The cipher algorithm should be passed as an extra argument
(of type ’enum MHD_GNUTLS_HashAlgorithm’). No longer supported,
using this value will cause
MHD_get_daemon_info to return NULL..
MHD_DAEMON_INFO_EPOLL_FD_LINUX_ONLY
Request the file-descriptor number that MHD is using for epoll. If
the build is not supporting epoll, NULL is returned; if we are using a
thread pool or this daemon was not started with
MHD_USE_EPOLL_LINUX_ONLY, (a pointer to) -1 is returned. If we are
using
MHD_USE_SELECT_INTERNALLY or are in ’external’ select mode, the
internal epoll FD is returned. This function must be used in external
select mode with epoll to obtain the FD to call epoll on. No extra
arguments should be passed.
MHD_DAEMON_INFO_CURRENT_CONNECTIONS
Request the number of current connections handled by the daemon. No
extra arguments should be passed and a pointer to a
union
MHD_DaemonInfo value is returned, with the
num_connections
member of type
unsigned int set to the number of active
connections.
Note that in multi-threaded or internal-select mode, the real number of current
connections may already be different when
MHD_get_daemon_info returns.
The number of current connections can be used (even in multi-threaded and
internal-select mode) after
MHD_quiesce_daemon to detect whether all
connections have been handled.
Obtain information about the given connection.
the connection connection is desired.
MHD_CONNECTION_INFO_CIPHER_ALGO
What cipher algorithm is being used (HTTPS connections only).
Takes no extra arguments.
NULL is returned for non-HTTPS connections.
MHD_CONNECTION_INFO_PROTOCOL,
Takes no extra arguments. Allows finding out the TLS/SSL protocol used
(HTTPS connections only).
NULL is returned for non-HTTPS connections.
MHD_CONNECTION_INFO_CLIENT_ADDRESS
Returns information about the address of the client. Returns
essentially a
struct sockaddr ** (since the API returns
a
union MHD_ConnectionInfo * and that union contains
a
struct sockaddr *).
MHD_CONNECTION_INFO_GNUTLS_SESSION,
Takes no extra arguments. Allows access to the underlying GNUtls session,
including access to the underlying GNUtls client certificate
(HTTPS connections only). Takes no extra arguments.
NULL is returned for non-HTTPS connections.
MHD_CONNECTION_INFO_GNUTLS_CLIENT_CERT,
Dysfunctional (never implemented, deprecated). Use
MHD_CONNECTION_INFO_GNUTLS_SESSION to get the
gnutls_session_t
and then call
gnutls_certificate_get_peers().
MHD_CONNECTION_INFO_DAEMON
Returns information about
struct MHD_Daemon which manages
this connection.
MHD_CONNECTION_INFO_CONNECTION_FD
Returns the file descriptor (usually a TCP socket) associated with this connection (in the “connect-fd” member of the returned struct). Note that manipulating the descriptor directly can have problematic consequences (as in, break HTTP). Applications might use this access to manipulate TCP options, for example to set the “TCP-NODELAY” option for COMET-like applications. Note that MHD will set TCP-CORK after sending the HTTP header and clear it after finishing the footers automatically (if the platform supports it). As the connection callbacks are invoked in between, those might be used to set different values for TCP-CORK and TCP-NODELAY in the meantime..
Values of this enum are used to specify what information about a daemon is desired.
MHD_FEATURE_MESSAGES
Get whether messages are supported. If supported then in debug mode messages can be printed to stderr or to external logger.
MHD_FEATURE_SSL
Get whether HTTPS is supported. If supported then flag MHD_USE_SSL and options MHD_OPTION_HTTPS_MEM_KEY, MHD_OPTION_HTTPS_MEM_CERT, MHD_OPTION_HTTPS_MEM_TRUST, MHD_OPTION_HTTPS_MEM_DHPARAMS, MHD_OPTION_HTTPS_CRED_TYPE, MHD_OPTION_HTTPS_PRIORITIES can be used.
MHD_FEATURE_HTTPS_CERT_CALLBACK
Get whether option #MHD_OPTION_HTTPS_CERT_CALLBACK is supported.
MHD_FEATURE_IPv6
Get whether IPv6 is supported. If supported then flag MHD_USE_IPv6 can be used.
MHD_FEATURE_IPv6_ONLY
Get whether IPv6 without IPv4 is supported. If not supported then IPv4 is always enabled in IPv6 sockets and flag MHD_USE_DUAL_STACK if always used when MHD_USE_IPv6 is specified.
MHD_FEATURE_POLL
Get whether
poll() is supported. If supported then flag
MHD_USE_POLL can be used.
MHD_FEATURE_EPOLL
Get whether
epoll() is supported. If supported then Flags
MHD_USE_EPOLL_LINUX_ONLY and
MHD_USE_EPOLL_INTERNALLY_LINUX_ONLY can be used.
MHD_FEATURE_SHUTDOWN_LISTEN_SOCKET
Get whether shutdown on listen socket to signal other threads is supported. If not supported flag MHD_USE_PIPE_FOR_SHUTDOWN is automatically forced.
MHD_FEATURE_SOCKETPAIR
Get whether a
socketpair() is used internally instead of
a
pipe() to signal other threads.
MHD_FEATURE_TCP_FASTOPEN
Get whether TCP Fast Open is supported. If supported then flag MHD_USE_TCP_FASTOPEN and option MHD_OPTION_TCP_FASTOPEN_QUEUE_SIZE can be used.
MHD_FEATURE_BASIC_AUTH
Get whether HTTP Basic authorization is supported. If supported
then functions
MHD_basic_auth_get_username_password() and
MHD_queue_basic_auth_fail_response() can be used.
MHD_FEATURE_DIGEST_AUTH
Get whether HTTP Digest authorization is supported. If
supported then options MHD_OPTION_DIGEST_AUTH_RANDOM,
MHD_OPTION_NONCE_NC_SIZE and functions
MHD_digest_auth_check(),
can be used.
MHD_FEATURE_POSTPROCESSOR
Get whether postprocessor is supported. If supported then
functions
MHD_create_post_processor(),
MHD_post_process(),
MHD_destroy_post_processor()
can be used.
Get information about supported MHD features. Indicate that MHD was compiled with or without support for particular feature. Some features require additional support by the kernel. However, kernel support is not checked by this function.
type of requested information
Returns
MHD_YES if the feature is supported,
and
MHD_NO if not.
Process escape sequences (’%HH’) Updates val in place; the result should be UTF-8 encoded and cannot be larger than the input. The result must also still be 0-terminated.
value to unescape (modified in the process), must be a 0-terminated UTF-8 string.
Returns length of the resulting val (
strlen(val) may be
shorter afterwards due to elimination of escape sequences).
Version
ECOS EXTENSION
This exception does not invalidate any other reasons why a work based on this file might be covered by the GNU General Public License. to readers acquainted
to the Tcl API: reference counting on
MHD_Connection
structures is handled in the same way as Tcl handles
Tcl_Obj
structures through
Tcl_IncrRefCount() and
Tcl_DecrRefCount().
POSTprocessor
POSTprocessor
POSTprocessor
This document was generated by Christian Grothoff on January 11, 2015 January 11, 2015 using texi2html 1.82. | http://www.gnu.org/software/libmicrohttpd/manual/libmicrohttpd.html | CC-MAIN-2015-11 | refinedweb | 7,030 | 55.95 |
David Soergel wrote:
> >Hi,
> > I've also been thinking about this. The current javac task doesn't
> >handle dependancies between java files. If you change an interface
> >then you have to clean and remake to check all files that use that
> >interface are consistant.
> >
> > The other part of this is that I don't want to have to specify the
> >dependancies in all cases. There should be a make-depend like
> >system.
>
> I'm not sure it makes sense to put a complicated dependency tracking
> thing in ant, with regard to .java files anyway, when "jikes +F"
> already does what you want. The way I use it is to make a dummy
> class with references to all the classes in my app, e.g. public class
> JikesDeps { myClass a; myOtherClass b; }, and then jikes +f
> JikesDeps.java. This way only things that have changed, and things
> that depend on things that have changed, get compiled.
>
But compiling Java is just one thing I want to do with ant. I want to run
XSLT over documents formed from multiple files, build package files etc.
etc. I can't use ant for this because XSLT tasks take too long to run
and I want to do it if, and only if, I need to do it.
jon. | http://mail-archives.apache.org/mod_mbox/ant-dev/200003.mbox/%3C38E4AB45.EE001E60@zeta.org.au%3E | CC-MAIN-2016-18 | refinedweb | 215 | 80.72 |
10
Shared Preferences.
Picture this: you’re browsing recipes and find one you like. You’re in a hurry and want to bookmark it to check it later. Can you build a Flutter app that does that? You sure can! Read on to find out how.
In this chapter, your goal is to learn how to use shared preferences to save important pieces of information to your device.
You’ll start with a new project that shows three tabs at the bottom of the screen for three different views: Recipes, Bookmarks and Groceries.
The first screen is where you’ll search for recipes you want to prepare. Once you find a recipe you like, just bookmark it and the app will add the recipe to your Bookmarks page and also add all the ingredients you need to your shopping list. You’ll use a web API to search for recipes and store the ones you bookmark in a local database.
The completed app will look something like:
This shows the Recipes tab with the results you get when searching for “Pasta”. It’s as easy as typing in the search text field and pressing the Search icon. The app stores your search term history in the combo box to the right of the text field.
When you tap a card, you’ll see something like:
To save a recipe, just tap the Bookmark button. When you navigate to the Bookmarks tab, you’ll see that the recipe has been saved:
If you don’t want the recipe any more, swipe left or right and you’ll see a delete button that allows you to remove it from the list of bookmarked recipes.
The Groceries tab shows the ingredients you need to make the recipes you’ve bookmarked.
You’ll build this app over the next few chapters. In this chapter, you’ll use shared preferences to save simple data like the selected tab and also to cache the searched items in the Recipes tab.
By the end of the chapter, you’ll know:
- What shared preferences are.
- How to use the shared_preferences plugin to save and retrieve objects.
Now that you know what your goal is, it’s time to jump in!
Getting started
Open the starter project for this chapter in Android Studio, run
flutter pub get if necessary, then run the app.
Notice the three tabs at the bottom — each will show a different screen when you tap it. Only the Recipes screen currently has any UI showing. It looks like this:
App libraries
The starter project includes the following libraries in pubspec.yml:
dependencies: ... cached_network_image: ^2.3.2+1 flutter_slidable: ^0.5.7 flutter_svg: ^0.19.0 flutter_statusbarcolor: ^0.2.3
Saving data
There are three primary ways to save data to your device:
Why save small bits of data?
There are many reasons to save small bits of data. For example, you could save the user ID when the user has logged in — or if the user has logged in at all. You could also save the onboarding state or data that the user has bookmarked to consult later.
SharedPreferences
shared_preferences is a Flutter plugin that allows you to save data in a key-value format so you can easily retrieve it later. Behind the scenes, it uses the aptly named SharedPreferences on Android and the similar UserDefaults on iOS.
shared_preferences: ">=0.5.8 <2.0.0"
flutter pub get
Saving UI states
You’ll use shared_preferences to save a list of saved searches in this section. Later, you’ll also save the tab that the user has selected so the app always opens to that tab.
Adding an entry to the search list
First, you’ll change the UI so that when the user presses the search icon, the app will add the search entry to the search list.
import 'package:flutter/material.dart';
import 'package:shared_preferences/shared_preferences.dart'; import '../widgets/custom_dropdown.dart'; import '../colors.dart';
class _RecipeListState extends State<RecipeList> {
static const String prefSearchKey = 'previousSearches';
bool inErrorState = false;
List<String> previousSearches = List<String>();
Running code in the background
To understand the code you’ll add next, you need to know a bit about running code in the background.
Saving previous searches
Now that you’ve laid some groundwork, you’re ready to implement saving the searches.
void savePreviousSearches() async { // 1 final prefs = await SharedPreferences.getInstance(); // 2 prefs.setStringList(prefSearchKey, previousSearches); }
void getPreviousSearches() async { // 1 final prefs = await SharedPreferences.getInstance(); // 2 if (prefs.containsKey(prefSearchKey)) { // 3 previousSearches = prefs.getStringList(prefSearchKey); // 4 if (previousSearches == null) { previousSearches = List<String>(); } } }
getPreviousSearches();
Adding the search functionality
To perform a search, you need to clear any all your variables and save the new search value. This method will not do an actual search just yet. Do this by adding the
startSearch() method after the
_buildSearchCard() method:
void startSearch(String value) { // 1 setState(() { // 2 currentSearchList.clear(); currentCount = 0; currentEndPosition = pageCount; currentStartPosition = 0; hasMore = true; // 3 if (!previousSearches.contains(value)) { // 4 previousSearches.add(value); // 5 savePreviousSearches(); } }); }
Adding a button to save a search
Next, you’ll give the user the power to save their searches by adding a save button.
IconButton( icon: const Icon(Icons.search), // 1 onPressed: () { // 2 startSearch(searchTextController.text); // 3 final currentFocus = FocusScope.of(context); if (!currentFocus.hasPrimaryFocus) { currentFocus.unfocus(); } }, ),
Expanded( // 3 child: TextField( decoration: const InputDecoration( border: InputBorder.none, hintText: 'Search'), autofocus: false, // 4 textInputAction: TextInputAction.done, // 5 onSubmitted: (value) { if (!previousSearches.contains(value)) { previousSearches.add(value); savePreviousSearches(); } }, controller: searchTextController, )), // 6 PopupMenuButton<String>( icon: const Icon( Icons.arrow_drop_down, color: lightGrey, ), // 7 onSelected: (String value) { searchTextController.text = value; startSearch(searchTextController.text); }, itemBuilder: (BuildContext context) { // 8 return previousSearches .map<CustomDropdownMenuItem<String>>((String value) { return CustomDropdownMenuItem<String>( text: value, value: value, callback: () { setState(() { // 9 previousSearches.remove(value); Navigator.pop(context); }); }, ); }).toList(); }, ),
Test the app
It’s time to test the app. Because you added a new dependency, quit the running instance and run it again (Note that you do not always need to restart when adding dependencies). You’ll see something like this:
Saving the selected tab
In this section, you’ll use shared_preferences to save the current UI tab that the user has navigated to.
import 'package:shared_preferences/shared_preferences.dart';
List<Widget> pageList = List<Widget>();
static const String prefSelectedIndexKey = 'selectedIndex';
void saveCurrentIndex() async { // 1 final prefs = await SharedPreferences.getInstance(); // 2 prefs.setInt(prefSelectedIndexKey, _selectedIndex); }
void getCurrentIndex() async { // 1 final prefs = await SharedPreferences.getInstance(); // 2 if (prefs.containsKey(prefSelectedIndexKey)) { // 3 setState(() { _selectedIndex = prefs.getInt(prefSelectedIndexKey); }); } }
getCurrentIndex();
saveCurrentIndex();
Key points
- There are multiple ways to save data in an app: to files, in shared preferences and to a SQLite database.
- Shared preferences are best used to store simple, key-value pairs of primitive types like strings, numbers, and booleans.
- An example use of shared preferences is saving the currently selected tab that a user is viewing, so that the next time the user starts the app, they’re brought to the same tab.
- The
async/
awaitkeyword pair let you run asynchronous code off the main UI thread and then wait for the response. An example is getting an instance of the
SharedPreferencesclass.
- The shared_preferences plugin should not be used to hold sensitive data. Instead, consider using the flutter_secure_storage plugin.
Where to go from here?
In this chapter, you learned how to persist simple data types in your app using the shared_preferences plugin. If you want to learn more about Android SharedPreferences, go to. For iOS, check UserDefaults. | https://www.raywenderlich.com/books/flutter-apprentice/v1.0.ea3/chapters/10-shared-preferences | CC-MAIN-2021-49 | refinedweb | 1,235 | 57.57 |
Finding Virtual Copies that Have Not Been Adjusted in Lightroom
The other day a customer asked me if there was a way to quickly find all of the virtual copies in their Lightroom library that didn’t have any adjustments applied in the Develop module so that they could delete them. (Unfortunately, someone had told them that they had to make virtual copies to all of their files before they made any changes and they now had hundreds of virtual copies that had never been adjusted/useless.)
I thought that it might be helpful to share the solution:
• Create a new Smart Collection in the Library module.
• Set the Criteria to the following:
–Copy name “isn’t empty” (to find all the virtual copies)
–Develop > Has Adjustments = “false”.
These 2 criteria will find all the Virtual Copies that do not have a Develop Adjustment.
Then, do one of two things. Either:
1) Select all of the Virtual Copies that you want to permanently delete and choose cmd+shift+option+return (mac) or ctrl+shift+alt+backspace (Windows). Note: this removes the Virtual Copies from the collection as well as deletes them from the library)
or:
2) Select all of the images in the Smart Collection.
• Use some type of “tag” such as the Reject Flag, a Star Rating, or a color label to somehow identify these virtual copies (something that you haven’t used to identify other images).
• Exit out of the Smart Collection by selecting “All Photographs” from the Catalog panel (or select a smaller subset by using the Folder Panel).
• Back in the grid view, filter for the virtual copies using the Library Filter bar at the top of the Grid view:
–Under Attributes, check the Virtual Copies icon.
–Then, add the attribute set in step 4 (flag or color etc.).
Note: I noticed that in the Lightroom 5 Beta, the Lens Correction attribute is not considered an adjustment…
Thanks Eric! | http://blogs.adobe.com/jkost/tag/snapshots-and-virtual-copies | CC-MAIN-2013-48 | refinedweb | 323 | 55.47 |
Overview
- What is
flashLightBoxInjector?
- Alternative (non-Flash) implementations of
flashLightBoxInjector
- Demos
- Download
- Version History
- License & Usage
- Installation/Configuration
- Static Code Example
- Dynamic Code Example (Step-by-step example)
- Dynamic Code Example (All-in-one example)
- Feedback/Help/Support
- Make a donation
What is
flashLightBoxInjector?
flashLightBoxInjector is a PrototypeJS class that bridges the gap between Flash and Lightbox2. Not only does
flashLightBoxInjector let you start an already existing Lightbox driven gallery (viz. static HTML), it also lets you dynamically build a list of images to show through Lightbox (viz. inject the needed HTML from within Flash).
Imagine a Flash movie loading a set of images from Flickr, showing all thumbnails. A click on the thumbnail will then fire up Lightbox to show that image (within its set). This is where
flashLightBoxInjector jumps in: after having loaded the images into your Flash file it automagically injects the needed HTML code into the current HTML document and then lets Lightbox know that this new set of images was included, enabling Lightbox to show them. And all this with the ease of a few calls made through Flash’s proprietary
ExternalInterface object. (See demo)
Looking for a version that works with ShadowBox instead of Lightbox? Head over to the PictureFlow project page and download the latest version in order to lay hands on
flashShadowboxInjector.
Alternative (non-Flash) implementations of
flashLightBoxInjector
The great thing about
flashLightBoxInjector is that its usage is not limited to Flash only, as the JavaScript can be called from anywhere you like
Imagine a website where you have a dropdown to select an image from and after a click on a button, Lightbox2 shows the selected image. Yes,
flashLightBoxInjector can be used for this purpose. (See demo2)
Demos
Download
The download of
flashLightBoxInjector includes a full example, including Flash Sources.
In order for this to work with Lightbox 2.0.4 (released 2008.03.09), you’ll need to make 1 tiny change to the lightbox.js file! Versions 2.0.x predating 2.0.4 will work “out of the box”
Latest Version
▼ Download flashLightBoxInjector 1.2
Old, Archived Versions
NOTE: it is advised that you use the latest version!
▼ Download flashLightBoxInjector 1.1
▼ Download flashLightBoxInjector 1.0
Don’t forget to read the License & usage and Installation/Configuration blocks on this page! 😉
Version History
Version 1.2 – 2007.11.22
- [add] Added a
prependElementfunction
- [add] Added a new, more impressive, example (Flash Polaroid Photo Gallery)
Version 1.1 – 2007.08.03
- [fix] Array passed into flashLightBoxInjector appeared reversed in Lightbox2
Version 1.0 – 2007.07.27 – * INITIAL RELEASE *
- Small coding of class, flash example, documentation, etc. resulting in a first release.
License & usage
The script is released under a creative commons Attribution-ShareAlike 2.5 license. Should you use the script within a commercial context please think about clicking the PayPal donate button.
Installation/Configuration
In order for this to work with Lightbox 2.0.4 (released 2008.03.09), you’ll need to make 1 tiny change to the lightbox.js file! Versions 2.0.x predating 2.0.4 will work “out of the box”
- Make sure you’ve set up Lightbox2 correctly.
- Include
flashLightBoxInjector.jsin your HTML
headsection, underneath the Lightbox2 references:
<script type="text/javascript" src="js/flashLightBoxInjector.js"></script>
- That’s it, you’re done!
Static Code Example
If you already have a set of links in your HTML, only a minor change is needed: each element must be given an id.
<a href="images/image-1.jpg" rel="lightbox[roadtrip]" id="roadtripImage1">image #1</a> <a href="images/image-2.jpg" rel="lightbox[roadtrip]" id="roadtripImage2">image #2</a> <a href="images/image-3.jpg" rel="lightbox[roadtrip]" id="roadtripImage3">image #3</a>
From within Flash then
call
myFlashLightBoxInjector.start through
ExternalInterface along with the id of the linked picture as
parameter. If you’d want to show the second picture, then you’d be using this piece of code:
import flash.external.*; btnShowImage.onRelease = function() { ExternalInterface.call("myFlashLightBoxInjector.start", "roadTripImage2"); }
Dynamic Code Example (Step-by-step example)
Imagine that you’ve pulled an XML file from Flickr containing a set of pictures and that you’ve loaded all thumbnails into Flash.
flashLightBoxInjector provides you the option to automatically generate the needed HTML, so that Lightbox has knowledge of that gallery. Here’s what you have to do:
Before going through the steps needed, it’s needed for you to know that
flashLightBoxInjector automatically creates a
div-element with the id
flashLightBoxInjectionBox where it will store the HTML needed for Lightbox.
If you have a robust knowledge of coding Flash/Javascript, then you might want to skip this example, and immediately go to the All-in-one example
First you have to import
flash.external.* in your Flash file, enabling javascript calls from within flash, the proper way
import flash.external.*;
(yes, we could use
getUrl("javascript:...") to call javascript functions, but that cannot be trusted 100%)
- First call a
myFlashLightBoxInjector.reset()from within Flash, this will clear the contents of
flashLightBoxInjectionBoxif you don’t want previously injected elements to appear in the same set (when using the same set ID):
ExternalInterface.call("myFlashLightBoxInjector.reset");
- While looping through your set of images within Flash (and placing a thumbnail version of the image onto the Stage for example), call a
myFlashLightBoxInjector.appendElementfor each image:
ExternalInterface.call("myFlashLightBoxInjector.appendElement", linkToTheImage + "", titleOfTheImage + "", uniqueIdOfTheImage + "", nameOfTheSet + "");
Note that I’m appending an empty string to each parameter (viz. implicit casting to String), as Flash otherwise tends to freeze due to some weird reason.
Don’t forget to hook an
onReleaseevent to the thumbnail you’ve placed onto the Stage, which will call the
myFlashLightBoxInjector.startfunction
ExternalInterface.call("myFlashLightBoxInjector.start", uniqueIdOfTheImage + "");
- After you have looped throuh all of your images, call a
myFlashLightBoxInjector.updateImageList, so that Lightbox will know of the newly injected set
ExternalInterface.call("myFlashLightBoxInjector.updateImageList");
That’s it, you’re done!
If you notice that your images appear in the reverse order in Lightbox than the order you’ve inserted them in your Flash File, then use
prependElement instead of
appendElement in the code above (Requires fLBI 1.2)
Dynamic Code Example (All-in-one example)
A full piece of code might look like this (full workout in example included in the download)
function attachImagesToStage(photoArray:Array):Void { // reset myFlashLightBoxInjector ExternalInterface.call("myFlashLightBoxInjector.reset"); // loop photoArray for (i=0; i < photoArray.length; i++) { // attach new MC to Stage var mc:MovieClip = this.attachMovie("photoFrame", "photoFrame" + photoArray[i].id, _root.getNextHighestDepth()); // add image to MC, set x and y coordinates, etc. mc.loadImage(photoArray[i].thumb); mc._x = ((mc._width * (i+1)) - (mc._width / 2)); mc._y = 25 + Math.round((Stage.height - (mc._height*2)) * Math.random()); mc._rotation = 30 - (60 * Math.random()); // append element in DOM through myFlashLightBoxInjector.appendElement ExternalInterface.call("myFlashLightBoxInjector.appendElement", photoArray[i].url + "", photoArray[i].desc + "", "photoFrame" + photoArray[i].id + "", "mySetOfImages"); // hook onRelease event mc.onRelease = function() { // show Lightbox with this image ExternalInterface.call("myFlashLightBoxInjector.start", this._name + ""); } } // let Lightbox know stuff has changed ExternalInterface.call("myFlashLightBoxInjector.updateImageList"); }
Now build an array of the images you wish the load, each entry having an
id,
url and
desc property and pass that array through the function.
attachImagesToStage(myArray);.
bramus,
Please check out this link if you have time I pasted your code in as well and created a form, but its still not working any ideas?
@ Nick : you have the wrong lightbox version! Version 2.03.3 is required, as that version holds a
updateImageListfunction which is used by flashLightBoxInjector. 😉
bramus thank you for you help. I appreciate getting back to me I need to take a holiday as well. Anyway I’ll try updating to the new version this weekend. I’ll also be sure to send a donation to you once this is done your gonna save me alot of time
Bramus sorry to bother you I got it working and it works great. I was using my macbook, but today I got a call saying the formatting was wrong. So i brought it up on my windows machine and noticed in IE it all messed up are you aware of any bugs? If you see anything you can email me or respond on this Thanks
NICK
Nevermind I figured it out Thanks anyway
hi,
like to know if i can implement the inyector into a flash scroller which has several linkings driven by a external xml document.
thanxs & best
eduardo
Great script!
Just want to point out a “typo” in your ‘Static code example’. It’s almost nothing but I had some trouble with this for like half an hour before I realised what the problem was.
If you copy/paste the HTML code the id’s says “roadtripImage2” but in the AS code it says “roadTripImage2”, and that capital ‘T’ just messed it up for me.
Now you know 😉
Thx for a great script
René
hi,
im really looking forward to getting this running from my flash files.
im launching a .swf as full page with SwfObject. i dont have the links to the images embedded into the HTML, can i still use flashlightboxinjector?
Hi Liam, you sure can do that. FlashLightBoxInjector will automatically insert the needed (hidden) div element when loaded.
Then follow the instructions to insert the images from within flash (through FlashLightBoxInjector) into the HTML, hook the events within your Flash file (viz. the buttons/objects which will start the Lightbox) and everything will work as it should 🙂
On a sidenote: I’ve done this myself over at, for which I have created FlashLightboxInjector 😉
can someone help please?
my test page
i’m using the exact code from the “Static Page Example”.
the button in the swf file has the instance name of btnShowImage and the actionscript is as below
import flash.external.*;
btnShowImage.onRelease = function() {
ExternalInterface.call(“myFlashLightBoxInjector.start”,”roadTripImage2″);
};
i have a folder called images in the same directory containing
image-1.jpg
image-2.jpg
image-3.jpg
if i click on the links in the page, it works but if i click the flash button, i dont get the gallery. how come?
also i dont want the links on the page, so instead of the identifier can i but in the url of the image instead?
i am a total javascript novice. sorry
@ liam: you’re calling “roadTripImage2” from within your flash, yet your id’s on the a elements are “roadtripImageX” (notice the lowercase T) … either change one of the two and you’re set 😉
thanks for the lightning fast reply!
one small query though, why does my swf file disappear when the gallery launches? is it because im not using SwfObject?
felt i had to reply to the “What’s the deal with Scrubs?” entry below, hopefully you agree with me??
..p.s.
how do i hide the links? i dont want them showing on the page?
@ liam:
– your swf is hidden as Lightbox does this automatically. To not hide it, comment out lines #376 (which reads
hideFlash();) & #624 (which reads
showFlash();) from
Lightbox.jsby placing // in front of the lines.
– Didn’t get that comment on the scrubs thread :-S
– Looks like you’ve sorted out the hiding (for those not knowing: place them in a
divwith
display:none;applied to it)
Gotcha!
Aaaahh now i can go to sleep!! its 2.30am here in Ireland. (i dont know where you are)
thanks for all your help. il be getting a Credit card very soon, il make a donation!
It’s 3.30 here in Belgium now 😉
Tia for the donation 🙂
Bramus, outstanding job on
Did you especially customise the polaroid sorting effex by yourself or is it built into flashinjector ?
Do you have some sample code on how you got flashinjector to work for downloads in your download section ?
Thanks for the great mod and look forward to hearing a lot from me.
(wmode = transparent) + (text inputs) = living nightmare
OMFG! is there anyway round this? in my text fields, @ becomes “.
surely, someone at Mozilla or adobe has heard about this?
this fixes it..
keyPresser = new Object();
keyPresser.onChanged = function(intxt:TextField) {
if (34 == ((Key.getAscii())) || 64 == ((Key.getAscii()))) {
intxt.text = intxt.text.slice(0,intxt.text.length-1) +”@”;
}
};
Key.addListener(keyListener);
input_txt.addListener(keyPresser);
stop();
@ Roland: the polaroid sorting effect has nothing to do with
flashLightBoxInjector. As in the included exmaple it’s an XML (from Flickr) that is read in, then looped through and an array is built. The only difference between Trancefusion.be and the code-example provided is that photoArray is randomized before being passed to
attachImagesToStage😉
@ Roland bis : the downloads are normal getURL() calls, has nothing to do with
flashLightBoxInjector😉
@ Liam : encountered the same problem whilst developing trancefusion.be … 😛
Bramus, the example code in your download provides non-polaroid effect, non draggable, ie:fixed images.
I’m not able to see in operation the kind of functionality that appears on trancefusion.be. What am I missing ?
Are you using webuppers Polaroid Gallery on trancefusion ?
@ Roland: I thought you meant the randomizing … anywho, yes, it’s a modded (read:
flashLightBoxInjectorintegrated) version of the link you’ve posted 😉
Are you willing to share the code to that ? I’m willing to donate
Hi Roland, will knock up an example any time next week (going on a little holiday within a few hours and won’t be back till next week) 😉
Hi Bramus, any luck with that code example ?
Hi Roland, haven’t started on it yet as I’m quite busy with 3RDS-related jobs atm … sorry about that. But no worries, the example will be created 😉
ok, bramus – anxiously waiting…
Any luck yet with this Bramus ?
@Roland: check the download link … new version with new example 😉
I am testing this on a Mac and running Safari 3.0.4 displays the Lightbox as if it is going to come up (only the transparent background appears) but nothing ever comes up. I run it in Firefox and it works just fine. Any ideas on this one. Is it using a tag that Safari doesn’t like in the javascript? Any help would be greatly appreciated!
Thanks for the update.
The fla files included in the v1.2 source seem corrupted as Flash 8 gives me the error ‘unrecognised file format.’
I suspect zip corruption.
Can you please recheck & repost ?
having the same problem as Chas…
I took the first example, commented out the flickr XML and loaded my own image array. The thumbs show up fine, the background dims, and nothing ever comes up. I JUST tested it using the original example (which is fine), but every time I load my own images in the SWF the damn thing freaks out!
I am literally yelling at my computer because I can’t get this thing to work… HELP!
It appears that when I load the RSS feed from flickr it functions perfectly… yet even when I download that VERY SAME FEED from flickr and put it on my server as an XML file the injector stops functioning. Any ideas/insight with this one?
@ Chas, Adam: will take a look into that … must say that over at Trancefusion.be the images of 2007 (which are over 200 images, yet only 15 are shown) aren’t loaded from an XML but inserted by a loop (alle images are named image-X.jpg, where X ranges from 1 up to 200).
@ Adam bis: sure the headers are ok (UTF-8 it should be)?
@ Roland: Flash CS3 is required. Will post a Flash 8 version of the .fla
@ Roland : redownload flashLightBoxInjector 1.2, the Flash 8 compatible versions are included now 😉
Is there a way to use this with an already existing external xml file? instead of creating one and importing everything into an array? I have a flash thumbnail scroller that I want to open the images in lightbox, but everything I’ve tried has failed when it tries to access the external xml file to retrieve the images. Any thoughts? Thanks
THANK YOU SO MUCH! THIS IS EXACTLY WHAT I WAS LOOKING FOR! WHAT A RELIEF! I JUST DID A LITTLE DANCE AROUND MY OFFICE!
wow, I’m a total nerd….
Thanks for your powerful “injector” !
I apply it on my “PictureFlow” project . In fact, a flash CoverFlow (By coincidence, I saw tonight, 3RDS developed one too on De Leeslijst website)
@Brandon: yes, that’s perfectly possible. In the examples provided, it reads in an already existing external xml (from Flickr in this case) and then builds an array of it.
@Jacob: Glad to have helped 🙂
@osamwal: very nice work! Kudos!
Thank you for this awesome effect for flash!!
Now, my problem is that i’ve downloaded the latest version, and I have serious problems to use it with static code and images at the same folder.
Could you help me please?
Which code should I use?
Thank U very much!
Good stuff!
but it doesn’t works on Opera 9.24
Hi Bramus, is it possible to insert flashinjector into another existing flash movie ?
So the polaroid effect would appear in a panel within another flash movie.
Appreciate any help on this.
@ Kriz : didn’t test in Opera. Think it has to do with the implementation on how Flash is loaded into Opera. Will check it out.
@ Roland: that not possible, as Lightbox is HTML+CSS+JS and Flash is … well … Flash. The thing you’re looking for is a flash version of Lightbox; don’t know if that exists (although a clever search on Google will tell you quickly).
Hi,
I wanted to ask, if it’s possible to use lytebox () with the injector instead of lightbox2…I need lytebox because I work with iFrames and lightbox doesn’t support them…I tried already some things but it didn’t work…I would like to use lytebox in combination with pictureflow 2.4 () which is already working with lightbox2, so it shouln’t be such a problem because pictureflow 2.4 works already with your injector…
but I’m not getting it and so I ask you =), what do I have to do to make this work…finally it should work with my site: –> under “Jamathetics” –> “Pressefotos” … the gallery is already there, but the pictures shouldn’t open in the iFrame, they sould open over the whole page (the nice thing of light/lytebox =D)…
thank you for your work with the injector, for your time and maybe your help =)!
greez,
LuK
if (mc._name.indexOf("reflection") == -1) {
mc.onPress = function():Void {
if ((getTimer()-this.pressTime<=doubleClickRegister && this.pressTime) || !doubleClickURL) {
if (infostruc[this.cid].urlToGet) {
getURL(infostruc[this.cid].urlToGet, "_"+infostruc[this.cid].urlAction);
}
}
this.pressTime = getTimer();
current = this.cid+1;
updateInfo();
};
Currently I have that setup to link to an outside link, when clicking on an image, but I would like it to load the large image in light box.
you can use any of these variables:
auth, album, httpType, urlToGet, urlAction
Can anyone help me add this into my flash app?
I tried doing: but no go.
if (mc._name.indexOf("reflection") == -1) {
ExternalInterface.call("myFlashLightBoxInjector.reset");
ExternalInterface.call("myFlashLightBoxInjector.appendElement", infostruc[this.cid].httpType + infostruc[this.cid].art + "", photoArray[i].auth + "", "photoFrame" + infostruc[this.cid].art + "", "mySetOfImages");
mc.onPress = function():Void {
if ((getTimer()-this.pressTime<=doubleClickRegister && this.pressTime) || !doubleClickURL) {
if (infostruc[this.cid].urlToGet) {
ExternalInterface.call("myFlashLightBoxInjector.start",infostruc[this.cid].httpType + infostruc[this.cid].art + "");
}
}
ExternalInterface.call("myFlashLightBoxInjector.updateImageList");
this.pressTime = getTimer();
current = this.cid+1;
updateInfo();
};
@ LuK : what you’re looking for is to use Lightbox from within an iframe, yet targetting the parent window. Lytebox indeed can do this as I have read, yet a modded Lightbox can do this too. Both are untested though, hope you can figure it out (I’m currently very busy, so can’t help you right now). 😉
@ Chris : you’ve mailed me that you have found the solution already. Care to post it here? It might help other people out (t)here 😉
Early morning:
(Thought people might want an explanation as some I wouldn’t have understood without playing with the script.)
In aways the solution is if your not familiar with the script find the loop which goes through every image (I set up some text box and set the value to the image until i saw it looped through all of them)
Place the Reset function above the loop. In the loop add all your variables in, using the append function.
After the loop is finished add in the update or in my case there was a section to check, and once all the images were loaded it set a value this was were I placed mine.
As for setUrl,
just replace it with ExternalInterface.call(“myFlashLightBoxInjector.start”,this.cid + “”);
I used the id in the loop for the unique id, which worked out nicely.
But I found one flaw, on certain machines the script does not like to work locally. I tried, and tried to find a solutions. If I upload onto the web it works.. Maybe someone can tell me why or find a solution?
Chris
Hi Bramus!
Came upon your script as I look thru the Lightbox forum – I am looking to have an image in a form script included in my Image View via Javascript. Lightbox2 cant do it – can flashLightbox?
The reason I need the image wrapped in a tag is that on each image that opens at the site below (click on “Gallery”, then choose a piece of art), the site visitor needs to see a PayPal “Buy Now” button. Paypal wraps those images in a form tag, and I cannot get the Flash/Lightbox javascript call to utilize such a tag (only an {HREF=} is working (with correct carats of course).
Would love to hear if I could utilitize your script instead!
Thanks!
Drew
@Andrew: I see you’re using LightboxDelegate; which can be used too. Set the onclick of the button (type image) to call LightboxDelegate() with the correct parameters.
Hi…
I am a newbie as far as javascript goes, but i have been using actionscript to create my portfoliowebsite. When I discoved shadowboxing images, i figured that might be a nice, dynamic way of letting viewer look at my work, how ever, HELP!! I do not understand all the steps I must go thruough just to get this to work!
I am using actionscript 2.0 and Flash CS3.
My entire site is ONE (1) SWF, embedded into an HTML page in Dreamweaver.
I would like the option for a viewer to click one of my image thumb buttons, and run an “on(Release)” command to call this javascript into action, from the FLASH BUTTON, using images stored on my webserver.
What do I need to do? What files files from the flashlightboxinjector download need to be on the server, and where? Are there specific directories i need to create for this? In Dreamweaver, do I have to do extra HTML coding even tho my entire site is basically a flash movie? What would my code look like in AS 2.0 for my flash button? Any help would be greatly appreciated. I am trying to wrap up final revisions to my site
Thank You!!
I have got this to work, the problem I’m having is that my flash in the back ground is disappearing. Is there any way to prevent that?
Thank you
Hi Bramus!
Read your comment from Oct 27th, thanks for the fix.
Hi Bramus,
I had one issue while using your great script. Is there a compatibility Issue with Lightbox2.04? I’ve used your script with Lightbox2.03 and it works seamlessly, but there seems to be an issue regarding compatibility with MacOS and Firefox, so I wanted to upgrade to 2.04, which didn’t work at all for me… Any help would greatly be appreciated!
@Derek: in order to use flashLightBoxInjector with 2.0.4 you’ll need to make 1 tiny change to the lightbox.js source file. You’ll need to change the very last line from:
document.observe('dom:loaded', function () { new Lightbox(); });
to
document.observe('dom:loaded', function () { myLightbox = new Lightbox(); });
For some reason unknown to me, Lokesh has removed the instantiation into a variable. I’ve mailed him about this issue and hope to see it fixed in a newer version of Lightbox.
Regards,
Bram.
I was just wondering if with this lightbox source allows for the loading of html or php documents in the lightbox?
@Ryan: no that’s not possible.
for this to work do i have to use your lightbox js because i know of one that allows for the use of an html page to be opened in the lightbox?
hello bram, i have a urgent question for you. i saw your example with the lightbox loaded from a flash file. but in your example the swf is dinamically loaded from the web, from flickr, isn’t?
i would like to do the same thing but from a flash button.. so if i release the flash button (the final swf is inserted in an html simple page) i would like to launch a little pictures gallery.
can you send me a sample example please?
thank you aniway
my mail is [email protected]
In a comment above (10/07) you said if the swf is hidden (ie. no transparency to Lightbox background) then do this:
– your swf is hidden as Lightbox does this automatically. To not hide it, comment out lines #376 (which reads hideFlash();) & #624 (which reads showFlash();) from Lightbox.js by placing // in front of the lines.
I have the same problem with transparency (can’t see my flash file in the background), but I went to Lightbox.js and the line numbers don’t match any code dealing with Flash. In fact I can’t find any references to Flash anywhere in the js file. Any recommendations? Everything else works OK. I have some looping effects and sound in the full page Flash file. Could that be hosing up the transparency?
Fixed it…
I had to downgrade to V1.1 in order to be able to comment-out the flash related lines in the js file. All is good now. Transparency works great.
I think something is broken in V1.2 (Lightbox 2.04) that screws up transparency on full page flash sites.
@Taki: Given that the gallery is already there and you know the id of the image you want to start (prerably the first one), you’ll only need to call
ExternalInterface.call("myFlashLightBoxInjector.start", uniqueIdOfTheImage + "");where
uniqueIdOfTheImageof course is the ID of the first lightbox-link 😉
@ Jim: Will check that out; Thanks!
Hello Bramus! Thank you for the wonderful scripts.
I used the flash LightBox Injector on my website in order to display some of my work on the “Portfolio” section (icons hanging from a tree). I tested on FF and Safari and it runs fine however I got some comments that is not working on IE 7. I haven’t been able to find any comments from people with similar problems yet and since I have a Mac (and no IE 7 available) is hard for me to do any testing. Any ideas what is going on?
Any comments will be greatly appreciated…
Cheers,
-Paco
Hi Bramus,
I have a .swf file that I want to run in a lightbox and have tried lightwindow and another one but it won’t read my xml when open in the lightbox. Will flashlightboxinjector do it?
Thanks
Ben
@Whathell: hmmz, can’t really pinpoint that one but am seeing a JS error. You could try installing companion.js/debugbar (both IE plugins) in order to get some more information about the error.
@Ben: flashLightBoxInjector will indeed do it (tip: read this page its intro and/or check out the demo’s ;))
Hi Bramus,
Have you received a reply about the myLightbox variable instantiation that disappeared? I have numerous sites that I would like to update with Lightbox 2.04, and I don’t really want to put in hacks in the author’s code, except if this is a permanent change.
@Francois: Hmmz, can’t find anything back … can you post your question here in the thread?
Hi,
I need i little help.
I make a test with the “Static Code” and it works. But when i try to use the function “appendElement” it dont work, im calling the exactly id that i injected and they just make the screen dark and dont show the white window with the image. Take a look:
import flash.external.*;
stop();
ExternalInterface.call(“myFlashLightBoxInjector.appendElement”, “images/image-1.jpg”, “its a test”, “test”, “group”);
btnteste.onRelease = function() {
ExternalInterface.call(“myFlashLightBoxInjector.start”, “test”);
}
Hey, I like what youve done with the flashinjector. I can get it to work in IE and FF and everything.
But where I am stuck on is trying to call the Lightbox from a button, that is located in a Movie Clip on the main timeline
Ive tried allsorts of things.
_root.mcname.btnname.ExternalInterface.call(“myFlashLightBoxInjector.start”, “Edge2”);
ive tried just in the MC
on release :
ExternalInterface.call(“myFlashLightBoxInjector.start”, “Edge2”);
tried in the MC onrlease:
_root.ExternalInterface.call(“myFlashLightBoxInjector.start”, “Edge2”);
even tried to put the action onto the button itself.
Just cant get it to work.
But when I put my button on the main timeline it works great.
with simple blahbtn.on rlease ( ;
ExternalInterface.call(“myFlashLightBoxInjector.start”, “Edge2”);
Anyone have any ideas, I dont know how often people check here.
I just want the button thats in a MC to call up the lightbox.
Im struggling here.
@Allen, @Tom: check your Flash Export Settings … be sure to have at least Flash Player 8 selected (have noticed that ExternalInterface can’t be called upon in FP7) 😉
Bramus,
Is there a way to get this to work with LightWindow?
Thanks!
@Kenet: It’s possible … if you write your own handler class that is.
I’m aware of a version for ShadowBox, inspired upon the work I’ve done. Maybe that’s an alternative?
Hi Bramus!
I have a website build with Flash. In the main Flash file I use mx.controls.Loader to load and replace parts of the main file and one of the loaded files is a gallery.
Question: Is it possible to use the flashlightboxinjector on that gallery?
Preisler
Hi Bramus. First I’d like to congratulate you for your research and script, it’s just great!!!
I’m using the flashinjector in my portfolio () and it’s doing fine. If you can visit the link you can check it out. But I did a flash script that change somethings in the site according to the hour of the day. If you adjust your computer clock to something between 8 pm and 5 am you will see what i’m talking about. And when I have a Flash mask in that part of the site and I click a job and it have to open in the Lightbox it simply don’t show it up. Do you have any idea what I’m doing wrong? The script have a bug when you use a Flash Mask?
thanks in advance
Tiago
i stubled across your site from another site that said you were trying to make your lightbox injector work with photoflow.
I have done something similar you can check it at maybe youll find something you can use
Hey, everythiing is working fine in regards to loading dynamic images. However, if I substitute I try to load a swf instead of an image I get a broken link. Is it possible to load swfs? If so please advise how. Thanks, good work.
Hey,
flashlightboxinjector is a god send. You’ve ridded me of a huge headache. I have one problem though. I already had the images displayed in my flash clip. If I hard code an image id to call, for example roadtrip2, it works perfectly. I tried to do this, however, and won’t work.
private function onClick(event:MouseEvent):void {
lbExpand=event.currentTarget.name;
trace(“lbExpand: ” + lbExpand);
ExternalInterface.call(“myFlashLightBoxInjector.start”,lbExpand + “”);
}
lbExpand is a string. It contains myImage0, myImage1, myImage2…etc. Those are the id’s I’ve attached to the images in my html. If I replace lbExpand with say, myImage5, it loads myImage 5. Using lbExpand fubar’s it though. Any suggestions?
You can totally disregard that question. Lightbox will never work if you don’t specify the right directory for the images. Works perfectly. Thanks for this great tool.
Maybe I don’t really hate spam. Sorry for the trifecta but I do have a question. When lightbox kicks in, rather than the overlay fading in, it flashes in. Any idea what might be causing that?
Hello, I’m from Germany, sorry bout my bad english haha, I’ve got a problem with the Lightbox 2.04. I’ve got a Flash-Page and want to directly start the Lightbox Diashow from a textbutton, without havin thumbs, Javascript bumpin up on the same page, like not startin a new html. Short form: startin that Javascript from Lightbox 2.04 via Textbutton from Flash. Any way to realize it? THX
Hi, it´s awesome how u did the solution for calling lightbox roadtrip from flash, really awesome! The best what i´ve find. But i am noobie and ionno how i can do my flash gallery working with lightbox roadtrip. If can help me, please contact me by e-mail [email protected] and i will send u my simple flash gallery (working eith lightbox, but not working roadtrip). Thank you very much!
Hi, I have a flash site(several.hu/ujfox007), and works everything with lightbox. But if i use IE and open the lightbox, the sound in the flash disappear. In firefox everything is oké.
How can i do this problem?
Sorry my poor english:)
Hi,
first, I appologies for my english…
I’m trying to use your awesome script but after 2 days of researches, I really need some help.
I don’t understand what is the XML structure so I can use my own (and not a flickr link)
Hope anyone could help
Thanks a lot
I finally found a solution !!
It works great !
Thanks !
Maybe I’m wrong, but if you don’t want swf to disapear, you can change line 205 of lightbox.js (V1.2) from
$$(‘select’, ‘object’, ’embed’).each(function(node){ node.style.visibility = ‘hidden’ });
to
$$(‘select’, ‘object’, ’embed’).each(function(node){ node.style.visibility = ‘normal’ });
Bramus, any luck with the Opera 9 problem? I’ve noticed that it’s really only on Opera Mac. The Windows version displays Flash fine.
@kimweb:
Could you post the XML structure that you found the solution to? I don’t know coding at all, but cut & paste my way through. I don’t want to use the flickr link either. Do I need to comment “//” a specific code out? Thanks.
“Yeti”
Bramus, it’s the first time I use Lightbox. I’m using static code and have a fullscreen flash. The problem if that if I insert the links in the html, the show below the flash animation. Where should I place them if I want them to be hidden, but still available to be called from within the flash movie?
Thanks
Sorry Bramus, I should have read all the comments, I figured it out. Great script by the way!
When using the static code and adding
import flash.external.*;
to my ActionScript, I keep getting a syntax error on exporting:
import flash.external.*;
btnShowImage.onRelease = function() {
ExternalInterface.call(“myFlashLightBoxInjector.start”, “image1”);
}
Evrythign is set up perfectly, and LightBox works from an HTML link. I just can’t get Flash to cooperate. Running CS3.
@Bill: Make sure you export your SWF as Flash Player 8 compatible. Lower won’t work.
Hi Bramus,
I’m using this to launch lightbox from a thumbnail gallery that is loaded from an xml file. Everything is working except that no matter what thumbnail I click, lightbox always opens the first image in the xml file. I can’t figure it out so I thought I’d ask you. Here is my AS
import fl.containers.UILoader;
import caurina.transitions.*;
import flash.external.*;
var urlRequest:URLRequest = new URLRequest("pics.xml");
var urlLoader:URLLoader = new URLLoader();
var myXML:XML = new XML();
var xmlList:XMLList;
myXML.ignoreWhitespace = true;
urlLoader.addEventListener(Event.COMPLETE,fileLoaded);
urlLoader.load(urlRequest);
//--------holds the paths to the thumbnails-------
var arrayURL:Array = new Array();
//--------holds the paths to the big photos-------
var arrayName:Array = new Array();
//--------holds the thumbnail objects-------
var holderArray:Array = new Array();
//--------represents the number of collumns-------
var nrColumns:uint = 5;
//-------represents the container of our gallery
var sprite:Sprite = new Sprite();
addChild(sprite);
var thumb:Thumbnail;
//-------- the thumbnails container-------
var thumbsHolder:Sprite = new Sprite();
sprite.addChild(thumbsHolder);
/* loop through the xml file
populate the arrayURL, arrayName and position the thumbnalis*/
function fileLoaded(event:Event):void {
myXML = XML(event.target.data);
xmlList = myXML.children();
ExternalInterface.call("myFlashLightBoxInjector.reset");
for (var i:int=0; i<xmlList.length(); i++) {
var picURL:String = xmlList[i].url;
var picName:String = xmlList[i].big_url;
arrayURL.push(picURL);
arrayName.push(picName);
holderArray[i] = new Thumbnail(arrayURL[i],i,arrayName[i]);
holderArray[i].name = arrayName[i];
holderArray[i].buttonMode = true;
if (i<nrColumns) {
holderArray[i].y = 65;
holderArray[i].x = i*110+65;
} else {
holderArray[i].y = holderArray[i-nrColumns].y+110;
holderArray[i].x = holderArray[i-nrColumns].x;
}
thumbsHolder.addChild(holderArray[i]);
ExternalInterface.call("myFlashLightBoxInjector.appendElement", xmlList[i].big_url + "", "persons");
thumbsHolder.addEventListener(MouseEvent.CLICK, calllightbox);
}
function calllightbox(event:MouseEvent):void{
ExternalInterface.call("myFlashLightBoxInjector.start", this._name + "");
trace("lightbox called")
}
}
ExternalInterface.call("myFlashLightBoxInjector.updateImageList");
my xml is structured like this:
thumbnails/ext1.jpg
bigimages/ext1.jpg
thumbnails/ext2.jpg
bigimages/ext2.jpg
Do I have to change my xml file? Or is there a problem in my AS. Sorry if the answer is obvious, I suck at coding but I’m getting better. Any help would be greatly appreciated.
Thanks
Sorry the tags in my xml file structure didn’t show up like I thought they would. Here is the structure with braces instead of brackets:
(images)
(image)
(url)thumbnails/ext1.jpg(/url)
(big_url)bigimages/ext1.jpg(/big_url)
(/image)
(image)
(url)thumbnails/ext2.jpg(/url)
(big_url)bigimages/ext2.jpg(/big_url)
(/image)
(/images)
Thanks
Hi Bramus:
Pardon my caveman question; is this compatible with AS3?
Thanks,
John
Is there any one to modify the code below so that I can place on an object’s actionscript such as a Button?
btnShowImage.onRelease = function() {
ExternalInterface.call(“myFlashLightBoxInjector.start”, “roadTripImage2”);
}
to
on(release) {
}
Thanks.
hi, is there a version of flashLightBoxInjector that would work with Slimbox2?
hi been trying hard to understand how lightbox 2 works with flash. But I’m so confused on what to do…
1. where do i put the files/which files?
2.where do u put your own sized images in so that they can be call when clicked?
3. basically need a step by step guide, NEED HELP BAD!!!!!
hopefully you can help me, cheers
hi i’ve implemented this semi-successfully into a gallery. it seems to work in safari on mac but not in firefox. i haven’t yet been able to test it on a pc. are there currently any bugs?
link using flashlightboxinjection 1.2 and lightbox 2.04
thanks
ok now it seems to work fine in firefox but still need to test on other computers. thanks for the great code!!
Hi bramus and the rest of the visitors
i would like to use lightbox (lightframe) to display other site pages from a flash file
What do i have to change to accomplish this ?
Also because of the newbie level in flash when you say “import flash.external.*;” do i have to substitute the * with something else or it’s the exact syntax
are this .js support or posibble we use in ‘multibox’ ?
regard from indonesia
I’m having trouble getting this to work (using static code). The links show up on my HTML page, all of which initiate lightbox fine, but the buttons in my swf don’t seem to want to work (and yes, i have changed the upper/lower case error for the id).
Could it be because I’m using AS3? (I’m currently calling myFlashLightBoxInjector.start through a function triggered by an event listener)
Hi,
thanks a ton for the injector, i am an amateur id say at Actionscripting. how can i load thumbnails from xml onto my flash file and then connect it to the lightbox. this should be really simple but cant figure out how to do it. please help. PLEASE.
Hi Bramus!
Thank you very much for the code. I implemented it in a site I am doing for my wedding just for fun. Funny thing is that lightbox turns off my music. Sounds work after I close the box but my timeline music is gone. Any suggestions?
Thanks again,
NickS
Hi,
Just wanted to check if this works with AS3 before I try to implement it.
Thanks!
Hi Bramus!
I’m currently working on a site for a photographer in flash and I’m having a real hard time trying to add lightbox into the site to show an added enlargement of the photos. I’ve been working on trying to figure this out for several days and have tried several people’s tutorials on how to do it but after countless headaches, I’m on my last leg. I think my problem might be that my flash file is somewhat complex. The page in which I want the button to show the lightbox is about 3 pages in from the main page. I’ve been trying to use the as to call the lightbox from that sub page, is this wrong? Should I be calling it from the main page? If so how do I link that to a button in another swf located inside that page called from a uiloader? I am a beginner when it comes to html (using dreamweaver) but I’ve done everything that I needed to in all these tutorials. I’ve gotten the lightbox to work directly from the html but It never seems to work when I try to do any of it from flash. With the as I was trying to use from your instructions for the lightboxinjector I kept getting error reports like ShowImage is not a definition keyword. I ended up using
import flash.external.*;
burm1e_btn.addEventListener(MouseEvent.CLICK,callJS);
function callJS(evt:MouseEvent):void{
ExternalInterface.call(“myFlashLightBoxInjector.start”,”burmesemigrants”);
}
which doesn’t give me any error messages but when I view the page in the browser with dreamweaver the button brings up a message in firefox (adobe flash player has stopped a potentially unsafe operation” and in safari it simply brings up a black blank page. This is what I have in html other than the lightbox2 lines to set that up
I took out the “image #1” in the projects, where I want the lightbox to appear is when you click on the detail image.) Please, I don’t know what else to try/do.
Hi..
I love this code and what it can do, but I just noticed that it’s not working for me in Internet Explorer. Every single other browser I checked seems to work out just fine. Did I miss a fix along the way that will allow this to work with IE? If so, can you pleeeaaseee help me figure out where it is and how to fix?
does this work with actionscipt 3?
Could anyone make it works with swishmax???
I need help
Lovin this just 2 things 🙂
How can I make the Thumbnail bigger like a 100 by 100?
And also so how can I get them to come in just in a line not all rotated?
Help would be great!
THANKS!
Ernie
Hei ppl!
Does anyone figure out the Internet explorer bug that stop my sound my flash site when a open a lightbox image?
Thanks in advanced!
Has anyone have to deal with transparency and this script hiding flash? i can add a
and it will show the bg but i cant get the lightbox to be transparent over my full screen flash movie
ok i figured out the problem with the transparency
in line 205 of lightbox.js theres a piece of code
$$(‘select’, ‘object’, ’embed’).each(function(node){ node.style.visibility = ‘hidden’ });
Which needed to be removed which i did and its not hiding my flash anymore the only problem i have now is that im not getting the shadowy overlay that surrounds the photo:
im just over looking one minor thing here. i know it..
I hope this helps pave the way for the people in my shoes atm. If you encounter or know a way to fix it please help.
okay i finally fixed it
line 52 in lightbox.js
I was going crazy trying everything that i had changed the line below to 0.2 and completely forgot about the change
when i rememeber going though all the steps when i set it back to default it fixed it. So make sure u leave this line defaulted @ 0.8 and take out the line above.
overlayOpacity: 0.8, // controls transparency of shadow overlay
i am having trouble with getting the flashlight box injector to work nothing happens when i click my button in my flash site that is suppose to call the injector here is my html and actionscript 3 code
html
Untitled Document
<!–
Content on this page requires a newer version of Adobe Flash Player.
<!–
actionscript
import flash.external.*;
officers.addEventListener(flash.events.MouseEvent.CLICK, lightbox);
function lightbox(event:MouseEvent) {
flash.external.ExternalInterface.call(“myFlashLightBoxInjector.start”, “myphotoimage1”);
return;
}
here is my html code
Hi Bramus,
read through all the comments and still stuck.
Lightbox 2 working fine in my html.
But Im confused as to what to do in my flash file.
Using the static code example but cant seem to set it up right in flash. Yes Im publishing with Flash Player 8.
What I dont understand is why you couldnt make the ‘simple’ example .fla file just use images found locally with none of the flickr/xml functionality, which quite frankly confuses me and is only really required for the more ‘complex’ examples.
Its a fantastic script, but like alot of people on the comments I dont know how to implement the actionscript. Please help.
Tom.
I’m having the same problem as shane. Doesn’t work with Internet Explorer.
Max Lopez, thanks so much mate. Saved alot of my time!!!
Open a lightbox from a Flash movie
There are too many problems with Lightbox, mostly if you use it from Flash! When it runs from a MovieClip call, it hides the whole site and there is no need to use the transparent image. Also, it stops all sounds when it run from Internet Explorer (which is the tool that 70% of users use…). It is a nice tool but… if it works! DO SOMETHING TO HELP US… AND STOP ASKING FOR A DONATION BECAUSE IT IS “NOT” WORKING FINE…!!
Yannis
Hey Bramus, what lines need to be commented out of the lightbox javascript to keep flash visible in the background using lightbox 2.04?
This is the first script that worked well in all browsers for me, thanks for the great work…
Hi
I have used this as3. Freddy is an mc on the stage
import flash.external.ExternalInterface;
ExternalInterface.call(“myFlashLightBoxInjector.reset”);
ExternalInterface.call(“myFlashLightBoxInjector.appendElement”, “”+””, “title1″+””, “uniqueId1″+””, “stopm”+””);
ExternalInterface.call(“myFlashLightBoxInjector.updateImageList”);
freddy.addEventListener(MouseEvent.CLICK, goAndGetIt);
function goAndGetIt(e:Event):void{
if (ExternalInterface.available)
{
ExternalInterface.call(“myFlashLightBoxInjector.start”, “uniqueId1″+””);
}
}
when I press freddy the whole stage goes gray – you can’t see the swf at all. There is no image either.
I appreciate your time
Edward
how to open html in lightbox instead of image?
Hi Bram,
is there a way to use your script with the Lytebox, too? Or does it only work with the Lightbox?
Best regards,
Daniel
Hi Bramus – love the scripting you’ve done – i however like a few noobs would like a simple static script which i can apply to a flash button that launches the lightbox script (and a specific image)
Many thanks
Al
Hi Bramus,
Sweet app, but I’m having problems implement it. I have the html working but not the flash part.
Here’s my actionscript:
/////////////////////////lightbox
import flash.external.*;
baseSEOmc.onRelease = function() {
ExternalInterface.call(“myFlashLightBoxInjector.start”, “roadTripImage2”);
}
just figured it out – you need both the html links and the flash button for this to work – you then just hide the html buttons
Hey Alistair,
I’m really stuck and need to get this thing done asap.
can you e-mail me?
Thanks!
I’m having a problem with lightbox2 and lightboxinjector.
I’ve used the same script, as stated above for the static code example as I am only using lightbox for a few buttons in Flash, but am getting script errors.
Script I’ve used:
import flash.external.*;
btnShowImage.onRelease = function() {
ExternalInterface.call(“myFlashLightBoxInjector.start”, “itpie_info_text_image”);
}
Error messages I get in Flash:
Statement must appear within on handler
import flash.external.*;
Statement must appear within on handler
btnShowImage.onRelease = function(){
I’ve noticed that there has been a few people asking this question, here and on Adobe’s site. But no one has addressed it openly yet.
If anyone can help that would be great.
Thank you.
This is the code that I am using for my buttons in AS 3. How do I work your code into this in order to view an image instead of a url?
import flash.events.MouseEvent;
var reqprint1:URLRequest = new URLRequest(“”);
btn2sub1.addEventListener(MouseEvent.CLICK,b21Click);
function b21Click(event:MouseEvent):void{
navigateToURL(reqprint1);
}
Hi,
I used it and the lightbox works in my flash site, except my whole video now takes ages to load and i tried everything and i think it’s because of lightbox – is that possible? is there a way to fix it? when i go to the page it is black and then the preloader starts from like 90%. This didn’t happen before and im going nuts trying to fix this 🙁 please help. thanks!
Ok so I’ve been doing a little digging around since my last post as I need this in a hurry and haven’t had a response yet.
I thought I would post my findings here to help anyone else who was having the same trouble.
So I found that a lot of people were confused with this ActionScript (AS):
import flash.external.*;
btnShowImage.onRelease = function() {
ExternalInterface.call(“myFlashLightBoxInjector.start”, “roadTripImage2”);
}
In Flash there is an error which says that the script has an error:
Statement must appear within on handler
import flash.external.*;
Statement must appear within on handler
btnShowImage.onRelease = function(){
What I found out was that you cannot apply this AS to a button directly, as you would with a .onrelease function etc.
What you need to do is to apply this LightboxInjector AS to the stage. So just click on the stage and then select the AS Window and then put the AS code in there.
The reason I found for this is that the import flash.external.*; command only works as a Static AS and when attached to a button it is classified as Dynamic AS. This is also the reason for the error in the line btnShowImage.onRelease = function(){.
This should eliminate all the error messages you are getting with the syntax in Flash.
The other thing you have to do, now that the AS relates to the stage and not the button you want it to work with is give the button an instance name. If you haven’t already.
The next step would be to go back to the AS on the stage and in the line where it says btnShowImage.onRelease = function() { and change the part btnShowImage to the same as the instance name for the button you want it to effect.
eg. buttoninstancename.onRelease = function() {
However, after doing all this to eliminate the Flash AS errors I can still not get the lightboxinjector to work with the button I want.
Please can I get some help with this.
And as before I’ll post my findings on here unless it is answered here.
Hope that helps someone.
Is it possible to use flash injector from flash to launch an external SWF?
Hello,
Great script, but I’m struggling to get any images to display for me.
Testing site:
When the limo stops, Click here to Enter displays, at which point user would click an the 1st image of the set of 26 should appear. But it doesn’t.
Any help would be greatly appreciated.
Thanks
got it working 🙂
I use foxycart in my site and the script seems to be clashing with foxycart files. It works perfectly without the foxycart files, but after adding foxycart script, nothing happens. Any help will be greatly appreciated!!!
Thanks in advance.
I got lightbox to work in FF and Safari, but it doesn’t work in Internet Explorer? I have the “id” attribute set, so what else am I doing wrong.
this is my code in FLASH:
import flash.external.ExternalInterface;
Print01_BTN.addEventListener(MouseEvent.CLICK,callJS);
function callJS(event:MouseEvent):void
{
ExternalInterface.call(“GroupDelegate”, “Thumb01” );
}
Like I said, it works fine in Firefox and Safari but not in Internet Explorer.
my site is
and it’s in the PRINT section.
Hi folks.
Anyone having problems triggering Lightbox from their swf’s mc buttons? I spent about 12 hours on this today pulling my hair out, searching across every forum I could find. Problem was that I had been testing it locally, and though the html links work fine for lightbox off my c drive, the flash triggers were doing nothing.
Loaded it all up online, voila! it works perfectly!!
Feel stupid now as it was such a simple solution!
Hi everyone,
is there any final solution (after 2 years !!!) for the flash swf file disappearing when the lightbox starts to open the images – mean, above mentioned lines 376 and 624 of lightbox.js version 1.1. – when the site is uploaded in IE…i got it working in Firefox but cant do it in Explorer…IE is putting the lightbox always under the swf!!!
example:
hi!
Sorry for the interruption. I have a problem I test this by using static code but when I click at at flash but it noting change.
I have attach file for you to check where is error << download this link
Thank you
Hi,
thanks for your great script!
Unlike most other users here I’m going for the “alternative usage” 🙂
I don’t want to use a drop down like you did, but I’d like to have a normal Input field where the user types something like “picture.jpg”, hits enter and picture.jpg will be opened with lightbox.
Should be pretty easy I guess but I’m stuck… 🙁
Hi,
Is it possible to use the injector for this carousel menu? It is very important for me! Please respond
Hi,
I already made this work for one flash button > one gallery.
Thanks a lot!
But now I want to have several flash buttons that open different lightbox galleries.
To do that, repeated the flash code, editing the new button instance name and the new file id (I also created another lightbox rel in the html):
import flash.external.*;
btn_bedroom1.onRelease = function() {
ExternalInterface.call(“myFlashLightBoxInjector.start”, “Bonjardim1” + “”);
}
btn_bedroom3.onRelease = function() {
ExternalInterface.call(“myFlashLightBoxInjector.start”, “Bedroom3-1” + “”);
}
But for some reason, the second button doesn’t work.
What am I missing?
Thanks in advance!
Hello, this looks great.
I am trying to launch “Lightbox Plus” plugin in WordPress with a Flash button.
Could this work? is there a working example for this or code modifications?
Thanks
Hi,
Thx for this tutorial, but I have to admit that didn’t worked for me, maybe I did something wrong. However, I succeed to use Shadowbox using this tutorial: with flash.external.ExternalInterface, seem to be more easier to implement it.
Hi there. I have a quick question; how do I modify the image size for this lightbox? I would like to make the featured content slideshow display larger (deeper images) on the homepage of The site is a WordPress site. Thank you so much for your response.
why you don’t put some examples file?
Finally, I found a good article about how to implement lightbox in Flash, I’ll give it a shot, hope that will work :D. Another tutorial about this matter can be found here:, maybe it will help someone. Cheers!
anyone got this to work in IE9 ?
Hi Bramus,
I am developing a website in which I have embed the flash object at the center of the HTML page. I have made all the pages in this way only. Now I want to show some images and videos on this flash content .i.e. I want to show images and videos at the center of my HTML page which is Flash object and I want to use the LightBox and VideoBox effect for showing the Images and Videos.
I have downloaded the example which you have put on your site but I didn’t help much.
Would highly appreciate if you can help me in this regard or can give me some pointer.
Thanks & regards,
Neeraj
Nice job with this! This was exactly what I was looking for. Is it possible to do a Google Maps lightbox thru Flash? Think it would be a complex build? | https://www.bram.us/projects/flashlightboxinjector/?replytocom=600 | CC-MAIN-2021-04 | refinedweb | 9,659 | 66.33 |
.
Back in the early 90s real-time multi-player games were pretty much unheard of. Computers were expensive and the only place you would find them connected to a network was at work and they would usually be running UNIX (or some manufacturer's proprietary operating system). Games were available but they were almost exclusively single player.
Then Steve Lehar released XBattle on the comp.sources.x newsgroup. This was a two-player battle simulation that was picked up by Greg Lesher and developed (over a number of years) into a multi-player real-time battle simulation game that was quite unlike anything seen before. And great fun to play..
Although I didn't use any of Greg's original code I wanted to carry on the spirit of XBattle and release my version as free software. An e-mail exchange with Greg verified he had no problem with this as long as I changed the name slightly to indicate that it is not an "official" follow-on from XBattle. Hence WinBattle.
The project is, of course, a very fun game. However, I wanted to release it as free software so that budding programmers have a (relatively) simple example of a way to build multi-player games. Just getting programs to talk to each other has always been hard work and WinBattle includes an easy to use mechanism that can be reused in other projects.:
The idea, of course, is to attack your opponent's troops, capture their bases and wipe them off the board.
To attack, just point your movement vectors at a cell occupied by the enemy. However, you'll find that you need to attack from more than one side to successfully occupy a cell.
You'll find client and server programs available for download (WinBattle_demo.zip). Run the server on a PC and start up to 6 clients on networked PCs with the command:
winbattle server computer name
Where server computer name is the name of the computer where the server is running.
Or create a shortcut that does the same thing (by the way, the default server computer name is localhost so if you want to try it out on just one PC just start the server and one or two clients on that machine to play). Press the start button on the server and away you go.
The server has a small number of options that are available in the dialog.
The Explore option means your troops have to scout out the terrain before you can see what's there. Turn it off and all players see the whole board from the start.
The Attrition option will cause troops to slowly waste away. This prevents the build up of totally massive amounts of troops.
The Group Bases option does just that. A player's bases will be positioned close together when this option is set and randomly scattered when it isn't.
The Disrupt option will cause enemy movement vectors to be cancelled when attacked. This allows a small number of troops to wreck supply lines that have to be constantly repaired.
The Hide Enemy Vectors option means you can only see an enemy's movement vectors if there are troops present in the cell (this provides a stealthier start to games.
The project was built with Visual Studio version 6 although it has also been tried with Visual Studio .Net. Should you want to compile the source code you only need to compile and build the client and server components. They will automatically pull in what they need from the common and game folders.).
What this means is that if you want to write a new game all you have to do is write the game code. You can re-use the client and server code pretty much as is. Of course, it isn't quite that simple but more on this later.
Note, although you can read this tutorial in isolation, to get the most from it you really should take a peek at the code in the client and server folders to get a feel for what's going on. Pretty much everything else can be ignored.
Anyway, as should be apparent by now, there are two programs used to run the game: a server and a client. The server actually runs the game, updating the board in real-time and sending the current state to all the clients. The client does very little. It displays the current state of play and accepts commands from the player for readability. As part of the dialog initialisation, the server starts two threads: game_handler and update_handler. The first thread handles commands going back and forth between the clients and the server and the second thread sends game updates to the clients once the game is actually started.
Actually establishing the network communication is probably the hardest part so let's begin by looking at the game_handler thread, the core of its operation is the following code:
Socket server(server_port);
while (true) {
server.listen();
for (int i = 0; i < max_players; i++) {
if (! clients[i].in_use) {
clients[i].connection = server.get_connection();
clients[i].in_use = true;
DWORD thread_id (0);
CreateThread(0, 0, client_handler,
reinterpret_cast<LPVOID>(i), 0, &thread_id);
break;
}
}
}
The code creates a socket telling it the port number to use. Port numbers are just a unique number so that many programs can use sockets without worrying about getting other program's messages. As long as the clients and servers both use the same number then everything should work just fine. The default for the WinBattle client and servers is set at 3333 as there isn't much chance of that number being in use on most PCs. However, if it is and you get a "port in use" error when you start the server, you can change it to any free port (you'll find that the port number is defined in the common folder in the file universal.h).
The thread then calls listen. This function will simply wait until some client program says it wants to communicate with the server on port 3333 (this is done from the client with a call to connect in client.cpp). Once a client has connected the listen function returns and the code runs through a table of player details to see if there is a free player position in the game. The code is currently set to handle up to 6 players (max_players) but that is easy to change (increase max_players and create additional colours for the new players in the Board class).
Once a free slot has been found the details of the client connecting are stashed away and a new thread (client_handler) is started to look after the new player. The game handler then loops back to the listen call where it will wait for more clients to connect (you'll find diagrams in the full tutorial showing the relationships of the various threads).
The client_handler thread creates a socket (called client) and initialises it with the details saved in the game thread so that it can talk to the newly joined client.
Socket client;
client.set_connection(clients[player].connection);
Then the client handler sits in a loop that performs the following:
while (true) {
string command;
client >> command;
for (int i = 0; i < num_commands; i++) {
if (command == command_list[i].command) {
command_list[i].function(client, player);
}
}
}
This just reads a command text string from the client connected to this thread, looks it up in a table of commands and, if it is found, calls the appropriate function to deal with that command. From the client end, the code to actually send some command is trivial, for example:
server << "some-command\n";
The very first thing that a client does when starting up is to start a thread to receive updates from the server update handler (the code for doing this is almost identical to that shown above). Once that thread is running, the client sends the following command to the server:
connect computer_name port
This command is used to tell the client handler which computer name the client is running on and which port the server should use to talk to the client (we could have just hard-coded a value as we did for the server but it's handy to run multiple clients on the same PC for testing and this lets us do this without messing about in the code). The server code for handling this command looks like this:
int port;
string hostname;
client >> hostname >> port;
client << player << "\n";
Socket * socket = (new Socket());
socket->connect(hostname.c_str(), port);
clients[player].socket = socket;
The first part of the code reads in the hostname and port and sends the player number back to the client. This tells the client which player he is in the game and is used to select the colour of his troops as the board is updated (amongst other things). The client_handler thread then creates a socket.
When the start button is pressed on the server dialog the following code is executed:
board.initialise(exploring, hidden);
for (int i = 0; i < max_players; i++) {
if (clients[i].in_use) {
board.setup_player(i, number_of_bases, group_bases);
}
}
for (int k = 0; k < max_players; k++) {
if (clients[k].in_use) {
Socket * socket = clients[k].socket;
(*socket) << "new-board\n";
board.transmit(socket);
}
}
game_running = true;
First, we ask the board to initialise itself, passing over some of the options from the dialog (this is when the terrain is generated). Then, for each player, we ask the board to set up that player (this is where bases are created).
Finally, we ask the board to copy itself to each of the clients over the socket connection we have established with the client. This deviates from our preferred streaming approach and uses the socket transmit function. I did start out streaming the board into and out of the socket but it was just too slow.
It's important to point out that the server has one copy of the board and every client has its own that is partly synchronised to the server master. This allows every client to have their own unique view on the board relating to what they can see (this feature is used to implement add a vector and send a command to that effect to the server. However, this is building knowledge of the game into the client, the server and the game classes themselves. This means that there could be a lot of work should we want to re-use the client or server code in a new project where keys and mouse buttons imply different commands.
The design aim is to make the client (and the server) as generic as we can. All they need to know is that they are playing a multi-user game. They don't need to know they are playing WinBattle or any other game. Consequently the client and server are dumb. If somebody clicks a mouse button they just blindly pass it on to the game classes who know what to do with it. In an ideal world, if you want to write a totally different multi-player game all you would have to do is change the game classes. You wouldn't have to touch the core client or server code at all.
However, back in the real world this isn't completely practical (although it is possible with some work). For example, the server dialog needs to know about the various game options so that they can be displayed and set. So, the pragmatic design goal is to keep the dependencies as small as we can and if you look at the code in the client and server directories you'll see that, although they know they have a game board, they know nothing else about it. For example, if we suddenly decided to make the board cells tiled octagons instead of hexagons then there would be no changes needed to either the client or the server code.
As the game progresses, the server update_handler thread periodically sends the updated state of the board to the clients. The code is as follows:
vector<Client>::iterator k;
for (k = clients.begin(); k != clients.end(); k++) {
if (k->in_use) {
Socket * socket = k->socket;
(*socket) << "update-board\n";
board.send_updates(socket);
}
}
board.end_of_updates();
This loops for each possible client. If a particular client is connected then we warn it that an update is about to follow with the update-board command and then send across the updates. Once all updates have been sent we let the board know that (with the call to end_of_updates so that it can prepare the next set).
The client code to deal with this is the rather boring:
board.get_updates(&inbound);
Note that neither the client nor the server has any idea what these updates are. They both just know that periodic updates are being exchanged.
OK, we've got all these threads up and running how do we handle clients and servers being terminated? Quite simply, if either stops it's polite enough to send a message to the other to that effect. For example, if the server is killed while clients are still running it runs through its list of connected clients and sends each one a message so that the client server handler thread can exit gracefully:
vector<Client>::iterator i;
for (i = clients.begin(); i != clients.end(); i++) {
if (i->in_use) {
*(i->socket) << "shut-down\n";
}
}
Similarly, if a client terminates it sends a message to the server so that the server client handler thread can close down and free up a slot for another client:
server << "disconnect\n";
The code that runs in the server when this command is received is as follows:
Socket * socket = (clients[player].socket);
(*socket) << "shut-down\n";
client.close();
socket->close();
free(socket);
clients[player].in_use = false;
ExitThread(0);
As the command to shut down comes from the main thread of the client we send a message to the client's other thread to ask it to shut down too. We close the sockets to release their resources and flag that we now have a free slot in our list of clients.
Note you will need to include socket.h in your code and incorporate socket.cpp as a module. You will also need to include the socket library ws2_32.lib in your link parameters. Now, what are all those things in the socket include file?
#include "exception.h"
C++ lets you handle errors with exceptions. Some people like them, some people don't. I do, so if I detect an error I throw an exception (the exception class that I use is included in the project). I recommend you use exceptions as) then the standard library will catch the thrown exception and quietly set the stream state to bad or fail (depending on the error). If you stream your data you must use the standard library error test functions fail() and bad() and not rely on an exception being caught.
void close ();
void connect (const char * const host, const int port);
void listen ();
These functions have been covered in the tutorial above. There's really not much more to say apart from the fact that if you give a port number of zero when creating a socket it will automatically allocate a free port number (you can see this being used in the client-side code). If you want to find out what number has been allocated use the following call:
int get_number ();
This is used by the client program to get its socket number so that it can tell the server what it is.
int bytes_read (bool reset_count = false);
int bytes_sent (bool reset_count = false);
You can read (and reset) the number of bytes sent and received over a socket. I used this when I wanted to display a progress bar while sending files over a socket in another project. call write_binary at the sender and read_binary at the receiver. You won't get data transfer between networked PCs much faster than that.
void set_trace (const char * filename);
If things are not working as expected and you can't figure out what's going wrong then ();
These functions let you transfer details from a socket established by a listen to a new one (so that the original socket can go back to listening). It was demonstrated in the game_handler thread description.
private:
Socket (const Socket & Socket); // No copying allowed
No copying of Sockets is allowed because I haven't written a copy constructor ... yet (and I'm not sure I want to). Why? The Socket class contains a buffer where it builds up text to send. Taking a copy (passing the socket as a parameter to a function) and adding to the buffer (inside the function) and then reverting to the original buffer (returning from the function call) is just too error prone. I just don't want to think about it. Does this mean you can't pass a socket as a function parameter? No, it doesn't, just pass it by reference rather than by copy. For example:
void my_function(Socket & socket);.
I've tried it out on Windows XP, 2000 and NT4. It should work on Windows 95 and later but I haven't been able to test that. There are probably plenty of bugs in the code so feel free to fix any that you come across :-). I'd also appreciate an e-mail letting me know of any that you find.
One problem I have seen is that sometimes when I compile it on my XP machine it seems to introduce a dependency on gdiplus.dll. I don't know why (yet), but if the programs bomb out on start-up it's a good chance they are looking for that DLL.
WinBattle is free software; you can redistribute it and/or modify it under the terms of the GNU General Public License (GPL) version 2 as published by the Free Software Foundation. You will find a copy of the GPL and the original XBattle license in the project notes folder.
After having two e-mail accounts rendered totally unusable by spam I don't publish my e-mail address on web pages or in newsgroups. However, you are welcome to e-mail me should you want. My address can be found in the file contact.txt in the notes folder in the source code. | https://www.codeproject.com/Articles/5706/WinBattle | CC-MAIN-2017-34 | refinedweb | 3,078 | 68.3 |
JWT in JSON Body¶
You can also pass the token as an attribute in the body of an application/json request. However, since the body is meaningless in a GET request, this is mostly useful for protecting routes that only accept POST, PATCH, or DELETE methods.
That is to say, the GET method will become essentially unauthorized in any protected route if you only use this lookup method.
If you decide to use JWTs in the request body, here is an example of how it might look:
from flask import Flask, jsonify, request from flask_jwt_extended import ( JWTManager, jwt_required, create_access_token, ) app = Flask(__name__) # IMPORTANT: Body is meaningless in GET requests, so using json # as the only lookup method means that the GET method will become # unauthorized in any protected route, as there's no body to look for. app.config['JWT_TOKEN_LOCATION'] = ['json'] attribute name where the JWT is looked for is `access_token`, # and can be changed with the JWT_JSON_KEY option. # Notice how the route is unreachable with GET requests. @app.route('/protected', methods=['GET', 'POST']) @jwt_required def protected(): return jsonify(foo='bar') if __name__ == '__main__': app.run() | http://flask-jwt-extended.readthedocs.io/en/latest/tokens_in_json_body.html | CC-MAIN-2018-34 | refinedweb | 186 | 54.56 |
)
}
//..
13 comments:
Welcome to concatenative programming :-)
USE: math.ranges
1 100 [a,b]
[ 2 mod 0 = not ] filter
0 [ + ] reduce
dup *
2 *
I am truly interested in Concatenative Programming. I have done some dabbling with Joy as well .. looking forward to some time to start with Factor. I wrote a couple of blogs on concatenative programming as well .. and
even better: implicit def any2Thrush[A](a: A) = Thrush(a)
This closely resembles FunctionN's andThen.
Very nice! I thought I've seen something like this, and I have: It's the $ operator from Haskell. You can even call it $ instead of 'into' if you like:
scala> (1 to 100).filter(_ % 2 != 0).foldLeft(0)(_+_) $ ((x: Int) => x * x)
res7: Int = 6250000
What I wrote was not correct as $ in Haskell normally has a diffent meaning (basically syntactic sugar to get rid of paranthesis). Although I saw a library somewhere that made it behave like the Thrush combinator shown here...
See also F#'s "forward pipe" operator.
I prefer F#'s pipeline operator (as mentioned in a previous comment):
implicit def pipelineSyntax[A](a: =>A) = new {
def |>[B](f: A => B) = f(a)
}
((1 to 100) filter { _ % 2 == 0 }) |>
(_.foldLeft(0) { _ + _ }) |>
(2 *)
Though, I will admit that it does work a lot better in a language which curries more heavily (e.g. ML derivatives like F#).
Wow, first time I saw a thrush, it's quite a beautiful pattern, thanks for posting, looking forward to more :)
With that brackets and the kind of reversed notion it looks similar to LISP not?
Thrush in Haskell:
thrush = flip (.)
Doesn't this beauty inspire you to learn Haskell?
If you have list comprehension, you can simply write:
sum [ x*x | x <- 1..100, odd x ]
Thrush is a special case of match!
(1 to 100).
filter(_ % 2 == 0).
foldLeft(0)(_ + _) match {
case x => x * x
}
Too bad you can't use match with an arbitrary partial-function, i.e., x match y == y(x) | http://debasishg.blogspot.com/2009/09/thrush-combinator-in-scala.html | CC-MAIN-2018-13 | refinedweb | 340 | 74.9 |
On Wed, Jan 21, 2009 at 01:17:32AM +0100, Arnd Bergmann wrote:> On Monday 19 January 2009, Joerg Roedel wrote:> > Impact: add debug callbacks for dma_{un}map_[page|single]> > In the discussion about "[PATCH] usb/mcs7830: Don't use buffers from> stack for USB transfers", I have raised the question of whether we can> add a check for the DMA address being on the stack, I guess this would> be the right place for it.> > Maybe you can add another check like:> > WARN_ON(is_kernel_stack(page_to_virt(page)));Good idea. This would be the right place for such a check.> Unfortunately, I can't think of a way to define a generic is_kernel_stack> function. On most architectures (all that put thread_info at the top of the> stack), something like this should work:> > #ifndef is_kernel_stack> static inline int is_kernel_stack(void *p)> {> return (unsigned long)p & ~(THREAD_SIZE - 1) == current_thread_info();> }> #endifHmm, this function is indeed required on all architectures. If you senda patchset which adds it I will add the check for stack addresses tothis debugging code :)Joerg | http://lkml.org/lkml/2009/1/23/123 | CC-MAIN-2014-10 | refinedweb | 175 | 52.83 |
13 July 2010 22:31 [Source: ICIS news]
HOUSTON (ICIS news)--US ethanol exports in May totalled 17.1m gal, rising by 61% from 10.6m gal a year earlier, the US International Trade Commission (ITC) said on Tuesday.
Ethanol exports in January through May totalled 141.4m gal, more than four times the 30.3m gal exported in the same period the year before, government data showed.
The figure includes shipments of denatured and undenatured, non-beverage ethanol.
The sustained increase in US ethanol exports was fuelled by continued growth in the production of the biofuel and relatively low US prices in the international market.
The jump in exports has triggered calls by ethanol industry groups for the ?xml:namespace>
“
The RFA is part of a coalition of | http://www.icis.com/Articles/2010/07/13/9376292/us-ethanol-exports-in-may-jump-61-year-on-year.html | CC-MAIN-2014-52 | refinedweb | 129 | 67.65 |
User account creation filtered due to spam.
The following code is compiled incorrectly with -O2:
#include <stdlib.h>
void f(int x) {
if (x < 0) {
if (-x > 0) {
exit(1);
}
}
}
int main() {
f(-0x80000000);
exit(0);
}
$ gcc foo.c; ./a.out
$ gcc -O2 foo.c; ./a.out
zsh: 4407 exit 1 ./a.out
$
-0x80000000 is going to overflow and for signed integers overflow is undefined. If you want signed integers to be defined to be wrapping use -fwrapv.
Wait a minute. 0x80000000 is unsigned. So -0x80000000 is well-defined, and
is 0x80000000 (unsigned). This is then converted to signed. Since 0x80000000
cannot be represented in signed, the result is implementation specific.
We document it to be -0x80000000. So the call is just fine.
It is the -x in f where x = 0x80000000 which is undefined as it overflows.
(In reply to comment #3)
> It is the -x in f where x = 0x80000000 which is undefined as it overflows.
Oh. I see. Right.
I see your point, but I still think there's a bug. Let me change the code slightly:
#include <stdlib.h>
#include <stdio.h>
void f(int x) {
long y;
if (x < 0) {
y = -x;
if (y > 0) {
printf("%d\n",y);
}
}
}
int main() {
f(-0x80000000);
exit(0);
}
$ gcc -O2 foo.c
$ ./a.out
-2147483648
so, we're in the y > 0 branch, but y is clearly < 0.
Pinskia is right, and this is just as undefined as your previous example (negating INT_MIN is just undefined, however you do it). All you've done is obfuscated things a bit more.
(In reply to comment #5)
> I see your point, but I still think there's a bug. Let me change the code
> slightly:
The code is still undefined, as you are comparing an overflowed variable to something.
-x is still undefined for x being 0x80000000 as it overflows and overflow signed integer is undefined runtime code.
Reopening to ...
Mark as a dup of bug 25329.
*** This bug has been marked as a duplicate of 25329 *** | https://gcc.gnu.org/bugzilla/show_bug.cgi?id=26824 | CC-MAIN-2016-36 | refinedweb | 337 | 85.59 |
April 11, 2020 Single Round Match 783 Editorials
PosNegDice
Keep two arrays: positiveValueCounts and negativeValueCounts.
In the first array, we will keep positive dices. We will keep negative dices in the second one. Then we will remove positive and negative die with the same value. It is, for each i, we will subtract min(positiveValueCounts[i], negativeValueCounts[i]) from positiveValueCounts[i] and negativeValueCounts[i].
Finally, we check if we have positive positiveValueCounts[i] where i <= T. Also we sum up all negativeValueCounts and return it as a point of stress.
public int[] evaluateRoll(int T, int[] positiveDice, int[] negativeDice) { // count the number of occurrences for each value int[] positiveValueCounts = new int[7]; int[] negativeValueCounts = new int[7]; for (int d : positiveDice) ++positiveValueCounts[d]; for (int d : negativeDice) ++negativeValueCounts[d]; // eliminate all equal pairs at once for (int d=1; d<=6; ++d) { int eliminated = Math.min( positiveValueCounts[d], negativeValueCounts[d] ); positiveValueCounts[d] -= eliminated; negativeValueCounts[d] -= eliminated; } // compute the answer by examining what remained int[] answer = {0, 0}; for (int d=1; d<=6; ++d) { if (d <= T && positiveValueCounts[d] > 0) answer[0] = 1; answer[1] += negativeValueCounts[d]; } return answer; }
BouncingBall
Hint: Simulate the process
From one hill to another, we first fall down and raise up again. We call this process a step. We keep the time and height at the start of each step, then step by step we check if we exceeded from the given time and print the answer.
Note that the maximum number of steps we need to process is not so much and small enough to pass the time limit. One can check it when g = 1000, h = 10, p = 10, t = 50, number of steps is 51.
The below code by misof is enough for understanding the math behind:
Hint: Simulate the process.
double freeFallDuration(double g, double h) { // given g and h, what is the duration of the free fall from height h to the ground? // this is then also the time the ball takes when thrown vertically upwards to height h (time reversal argument) // h = gt^2 / 2 => t = sqrt(2h/g) return Math.sqrt(2*h/g); } double freeFallPosition(double g, double h, double t) { // given g, h, t such that t <= freeFallPosition(g,h), // what is the position of the ball t seconds after the free fall from height h started? return h - g*t*t/2; } public double getPosition(int gCm, int h0, int p, int tGoal) { double t = 0; double h = h0; double g = gCm / 100.; while (true) { double tFall = freeFallDuration(g,h); if (t + tFall >= tGoal) { // we reach the goal time during the fall downwards double tDuringFall = tGoal - t; return freeFallPosition(g,h,tDuringFall); } t += tFall; // do the bounce, lose some height h *= (100 - p) / 100.; double tRise = freeFallDuration(g,h); if (t + tRise >= tGoal) { // we reach the goal time during the rise upwards double tDuringRise = tGoal - t; double tDuringFall = tRise - tDuringRise; return freeFallPosition(g,h,tDuringFall); } t += tRise; } }
CardboardBoxes
Assume length >= width.
Area of the sides is 2 * height * (width + length).
The other dimension of top flaps will be width/2, so their area is width * (width + length).
The same for the bottom.
So S = 2 * (width + length) * (width + height).
To illustrate this, you can actually cut out such a box from a (2L+2W) * (H+W) cardboard rectangle as shown below. Lines inside are cuts, dots are folds, asterisk edges have to be taped together. This is how you can really produce such boxes with minimum waste.
W L W L +----+---------+----+---------+ | | | | | W/2 + .. + . . . . + .. + . . . . + * . . . * * . . . * H * . . . * * . . . * + .. + . . . . + .. + . . . . + | | | | | W/2 +----+---------+----+---------+
So possible options of width + length are divisors of S / 2. We can find divisors of S / 2 in O(S). After fixing width + length = k, we know that width + height = S/k. Once we choose width the other two dimensions are fixed, and we can compute the number of valid widths in constant time.
Code by misof: long processKnownLplusW(long S, long LplusW) { long HplusW = S / LplusW; long maxW = Math.min( LplusW/2, HplusW-1 ); return maxW; } public long count(long S) { if (S % 2 == 1) return 0; S /= 2; long answer = 0; for (long d=1; d*d <= S; ++d) if (S % d == 0) { answer += processKnownLplusW(S,d); if (d < S/d) answer += processKnownLplusW(S,S/d); } return answer; }
ABBAReplace
Hint: Consider a similar process from the end to the beginning.
Direct simulation is ugly. We can visualize the process as “Bs want to go to the left”, but the process is complicated: e.g., there can be Bs that alternately move and have to stay in place.
There are two observations that can really simplify the solution. First, we can relax the original task by allowing some letters to stay in place instead of being swapped. The minimal number of turns clearly remains the same because greedily making all possible swaps produces one possible optimal solution for the new task. However, now there will be other optimal solutions, too, and those will be easier to construct.
Second, consider the new problem backwards. What do we have in the end? Something like “BBB…BAAA…”. Some of these Bs are in their right places, others need to move to the right. The rightmost B can start moving immediately and it will never be blocked. In the second step the rightmost two Bs can move, and so on. In this way, no B will ever get blocked by another one because the ones to its right started moving sooner and go farther right. Hence, we can simply compute each B’s travelling time as (the number of Bs to its right) plus (the number of steps it needs to make).
Code by misof:
public int countSteps(String Sprefix, int N, int seed, int threshold) { StringBuilder sb = new StringBuilder(Sprefix); long state = seed; long modulus = 1L << 31; while (sb.length() < N) { state = (state * 1103515245 + 12345) % modulus; if (state < threshold) sb.append("A"); else sb.append("B"); } String S = sb.toString(); ArrayList<Integer> bindices = new ArrayList<Integer>(); for (int n=0; n<N; ++n) if (S.charAt(n) == 'B') bindices.add(n); int BC = bindices.size(); int maxtime = 0; for (int b=0; b<BC; ++b) { int bdest = bindices.get(b); if (bdest == b) continue; maxtime = Math.max( maxtime, BC-1-b + bdest-b ); } return maxtime; }
RecursiveTournament
Hint: Calculate the answer for k = 1.
Let’s think about what a subgraph looks like? It consists of several groups of vertices say a1, a2, …, am, where for each vertex like v in ai, and u in aj v has a directed path to u if and only if i <= j.
It looks like a chain (maybe consists of one group, i. e. m = 1). Vertices in group a1 are strongly connected (similar for a2, a3, …, am), every vertex from a1 has a directed edge toward every vertex in a2, a3, …, am. Every vertex from a2 has a directed edge toward every vertex in a3, a4, …, am. Also, there is no edge from v in ai toward u in aj where i > j, otherwise, they can create a larger group together.
From the constraints, we straightly jump to dp on bitmasks! For each mask, let’s calculate part[mask][]. part[mask][v] (that v is present in the mask) is the group (ai) that v is present in it; when showing the vertices in the mask as the above format.
Let’s calculate part[mask]. Take a vertex like v from the mask. Let omask be a mask excluding v (omask = mask ^ (1 << v)). We need to find the rightmost group (with the largest index) that has a vertex that has an edge toward v, name it R. Similarly, find the leftmost group (with the lowest index) that has a vertex that v has an edge toward it, name it L. If R < L, v creates a new group. Otherwise, v will merge groups [L, R] together and join them.
In the end, we check if part[mask][] is 1 for all of the present vertices then mask is an SCC.
Now, let’s solve the general problem when k is not necessarily 1. Consider an SCC in the input graph with size x: v1, v2, …, vx. In the code below s[x] stands for the number of times it appears in the big tournament graph. What is s[x]?
How many vertices start with v1? b ^ (k – 1). Same for v2, v3, …, vx. We choose a non-empty subset of vertices from vertices starting with v1, another non-empty subset from vertices starting with v2, … . The number of ways to choose x vertices we counted here equals (2 ^ (b ^ (k – 1)) – 1) ^ x. Now we just counted the number of subsets of vertices in the big tournament such that at least two of them differ in the first bit. We go further for the second, third, …, k-th bit. When calculating the number for i-th bit, b ^ (i – 1) * (2 ^ (b ^ (k – i – 1)) – 1) ^ x. We have b ^ (i – 1) ways to choose the prefix for vertices.
In the end, we are able to calculate s[x] for each x in the range [1, n].
Overall time complexity is O(n * 2^n + nk).
Here is the code by lg5293:
int mod = 998244353; int b; int k; long ans; long[] s; boolean[][] mat; int max(int[] arr) { int ret = arr[0]; for (int x : arr) ret = Math.max(x, ret); return ret; } long mod_exp(long b, long e, long mod) { long res = 1; while (e > 0) { if ((e & 1) == 1) res = (res * b) % mod; b = (b * b) % mod; e >>= 1; } return res % mod; } public void dfs(int[] part, int mask, int idx) { if (idx == b) { if (Integer.bitCount(mask) > 1 && max(part) == 1) { ans += s[Integer.bitCount(mask)]; if (ans >= mod) ans -= mod; } return; } dfs(Arrays.copyOf(part, part.length), mask, idx+1); if (mask == 0) { part[idx] = 1; dfs(part, mask | (1 << idx), idx+1); return; } int lowest = b, highest = 0; for (int i = 0; i < idx; i++) { if (((mask >> i) & 1) == 1) { if (mat[i][idx]) lowest = Math.min(lowest, part[i]); else highest = Math.max(highest, part[i]); } } if (lowest == highest) { part[idx] = lowest; } else if (lowest > highest) { // highest+1 == lowest for (int i = 0; i < idx; i++) { if (part[i] >= lowest) part[i]++; } part[idx] = highest + 1; } else { // lowest < highest for (int i = 0; i < idx; i++) { if (part[i] >= lowest) { if (part[i] > highest) { part[i] += lowest - highest; } else { part[i] = lowest; } } } part[idx] = lowest; } dfs(part, mask | (1 << idx), idx + 1); } public int count(String[] graph, int k) { b = graph.length; mat = new boolean[b][b]; for (int i = 0; i < b; i++) { for (int j = 0; j < b; j++) { mat[i][j] = graph[i].charAt(j) == 'Y'; } } s = new long[b + 1]; for (int j = 0; j < k; j++) { long r = mod_exp(b, k - j - 1, mod); long mult = mod_exp(2, mod_exp(b, j, mod - 1), mod) - 1; for (int i = 0; i <= b; i++) { s[i] = (s[i] + r) % mod; r = r * mult % mod; } } ans = mod_exp(b, k, mod); dfs(new int[b], 0, 0); return (int)ans; }
a.poorakhavan
Guest Blogger | https://www.topcoder.com/blog/single-round-match-783-editorials/ | CC-MAIN-2022-40 | refinedweb | 1,860 | 71.44 |
PyParallel: A Fast Parallel Version of Python
PyParallel is a research project by Trent Nelson. Its goal is to bring the power of Windows’ I/O Completion Ports to Python in a way that allows for high performance asynchronous support.
Python’s asynchronous support is somewhat problematic. It is designed around the Unix/Linux idea of synchronous, non-blocking I/O. This is where a thread continuously polls for incoming data and then dispatches it accordingly. While Linux is tuned for this pattern, on a Windows machine this is disastrous for performance. It is really expensive to copy the data from the polling thread to the thread that will actually process the work.
So what PyParallel delivers instead is true asynchronous I/O using the native I/O Completion Ports (IOCP). Under the IOCP model there is one thread per core. Each thread handles completing the I/O request (e.g. copying data from the network card) and executes the application level callback associated with it.
This alone isn’t enough to scale out Python; the GIL or Global Interpreter Lock also needs to be addressed. Otherwise you are still limited to one thread executing at a time. Replacing the GIL with fine-grained locks was found to be even worse and software transactional memory as seen in PyPy usually ends up with 1 thread making progress and N-1 threads continuously retrying. So something else is needed.
For the PyParallel team that something else is to not allow free threading. That is to say, the application cannot arbitrarily create new threads. Instead, parallel operations are tied to the async callback mechanism and the concept of a parallel context.
Before we dive into parallel contexts, we need to look at the converse. When the parallel context isn’t running then the main thread is running and vice-versa. The main thread is what you think of for normal Python development. It holds the GIL and has full access to the global namespace.
Conversely, a parallel context has read-only access to the global namespace. This means that the developer needs to pay attention to whether something is a main thread object or parallel context object. (COM programmers dealing with apartment threading models know this pain all too well.)
For non-I/O tasks the main thread queues up tasks using the async.submit_work function. Then it switches to the parallel context using the async.run function. This suspends the main thread and activates the parallel interpreter. Multiple parallel contexts can run at the same time with the Windows OS handling the thread pool management.
Parallelism with a GIL
At this point it is important to note that multiple processes are not created. Though this technique is commonly used in Python development, PyParallel keeps everything in one process to reduce cross-process communication costs. Normally this isn’t allowed because the CPython interpreter isn’t thread safe. This includes:
- Global statics are frequently used
- Reference counting isn’t atomic
- Objects are not protected by locks
- Garbage collection isn’t thread safe
- Interned string creation isn’t thread safe
- The bucket memory allocator isn’t thread safe
- The arena memory allocator isn’t thread safe
Greg Stein tried to fix this by adding fine grain locking to Python 1.4, but his project was rejected because it caused a 40% slowdown in single-threaded code. So Trent Nelson decided on a different approach. While in the main thread, the GIL operates as normal. But when running in a parallel context, thread safe alternatives to the core functions are used instead.
The overhead for Trent’s approach is 0.01%, much better than Greg’s attempt. As for PyPy’s software transactional memory, that has an overhead cost of roughly 200 to 500% for the single thread model.
An interesting feature of this design is that code running in a parallel context doesn’t need to acquire a lock to read from objects in the global namespace. But again, it is in a read-only capacity.
PyParallel doesn’t have a garbage collector
In order to avoid dealing with locks for memory allocation, access, and garbage collection, PyParallel uses a share nothing mode. Each parallel context gets its own heap and no garbage collector. That’s right, there is no garbage collector associated with a parallel context. So here’s what happens.
- Memory allocation is done using a simple block allocator. Each memory allocation just bumps the pointer.
- As needed, new pages of either 4K or 2MB in size are allocated. The parallel context’s large pages setting controls this.
- No reference counting is used.
- When the parallel context terminates, all pages associated with it are freed at one time.
This design eliminate the cost of a thread-safe garbage collector or thread safe reference counting. Plus it allows for the aforementioned block allocator, which is probably the fastest possible way to allocate memory.
The PyParallel team thinks they can get away with this design because parallel contexts are meant to be short lived and finite in scope. A good example would be a parallel sorting algorithm or a web page request handler.
In order to make this work, objects created in a parallel context cannot escape into the main thread. This is enforced by having the read-only access to the global namespace.
Reference Counting and Main Thread Objects
At this point we have two types of objects: main thread objects and parallel context objects. Main thread objects are reference counted because at some point they are going to need to be deallocated. Parallel context objects are not reference counted. But what about the interaction between the two?
Well since the parallel context thread cannot modify a main thread object, it cannot alter the main thread object’s reference count. But since the main thread garbage collector cannot run while parallel contexts are running, that’s not a problem. By the time the main thread GC is started, all of the parallel contexts have been destroyed and there is nothing pointing from them back to the main thread objects.
The end result of all this is that code executing in a parallel context is actually faster than code executing on the main thread.
Parallel Contexts and Async I/O
The memory model discussed above starts to break down when you start talking about asynchronous I/O calls. These calls can keep a parallel context alive far longer than the system was designed for. And in the case of something like a web page request handler, there could be an unlimited number of calls.
To deal with this problem, Trent added the concept of snapshots. When an asynchronous callback starts a snapshot of the parallel context’s memory is taken. And the end of the callback the changes are reverted and the newly allocated memory is freed. Again, this is good for something stateless like a web page request handler but bad if you need to retain data.
Snapshots can be nested up to 64 layers deep, but Trent didn’t go into details about how that works.
Balancing Synchronous and Asynchronous I/O
Asynchronous I/O isn’t free. When you want to get the most throughput with the least amount of latency, synchronous I/O can actually be faster. But that is only true if the number of concurrent requests is less than the number of available cores.
Since the developer doesn’t necessarily know what the load is going to be at any given time, expecting him to make the decision can be unreasonable. So the PyParallel offers a socket library that makes the decision at run time based on the number of active clients. As long as the number of active clients is less than the number of cores, synchronous code is executed. If the client count exceeds it the library automatically switches to asynchronous mode. Either way the application code is ignorant of the change.
Asynchronous HTTP Server
As part of the proof of concept, PyParallel comes with an asynchronous HTTP server based on the SimpleHttpServer that is part of stdlib. One of the key features is support for the Win32 function TransmitFile, which allows data to be sent directly from the file cache to the socket. PyParallel’s HTTP server allows prepending and postpending data to this in an asynchronous manner.
Future Plans
In the future Trent wishes to continue to improve the memory model by introducing a new set of interlocked data types and adding the use of context managers to control memory allocation protocols.
Integration with Numba is also in the works. The idea is to launch Numba asynchronously and atomically swap out CPython for natively generated code when Numba completes.
Another planed change is support for pluggable PxSocket_IOLoop endpoints. This would allow different protocols to be chained together in a pipeline fashion. Where possible he wants to use pipes instead of sockets for this to reduce the amount of copying necessary between steps.
For more information see Trent Nelson’s presentation, PyParallel - How We Removed the GIL and Exploited All Cores (Without Needing to Remove the GIL at all)..
This is great
by
Gary Robinson
So this is exactly what I was looking for. Numba will just make it all the better.
I had decided that if I ever have to do that kind of work again, I'd try Go. But if PyParallel works well enough, it may be exactly what I | http://www.infoq.com/articles/PyParallel/ | CC-MAIN-2015-18 | refinedweb | 1,579 | 63.8 |
Acquire and Prepare the Ingredients - Your Data
In this chapter, we will cover:
- Working with data
- Reading data from CSV files
- Reading XML data
- Reading JSON data
- Reading data from fixed-width formatted files
- Reading data from R files and R libraries
- Removing cases with missing values
- Replacing missing values with the mean
- Removing duplicate cases
- Rescaling a variable to specified min-max range
- Normalizing or standardizing data in a data frame
- Binning numerical data
- Creating dummies for categorical variables
- Handling missing data
- Correcting data
- Imputing data
- Detecting outliers
Introduction
Data is everywhere and the amount of digital data that exists is growing rapidly, that is projected to grow to 180 zettabytes by 2025. Data Science is a field that tries to extract insights and meaningful information from structured and unstructured data through various stages such as asking questions, getting the data, exploring the data, modeling the data, and communicating result as shown in the following diagaram:
Data scientists or analysts often need to load or collect data from various resources having different input formats into R. Although R has its own native data format, data usually exists in text formats, such as Comma Separated Values (CSV), JavaScript Object Notation (JSON), and Extensible Markup Language (XML). This chapter provides recipes to load such data into your R system for processing.
Raw, real-world datasets are often messy with missing values, unusable format, and outliers. Very rarely can we start analyzing data immediately after loading it. Often, we will need to preprocess the data to clean, impute, wrangle, and transform it before embarking on analysis. This chapter provides recipes for some common cleaning, missing value imputation, outlier detection, and preprocessing steps.
Working with data
In the wild, datasets come in many different formats, but each computer program expects your data to be organized in a well-defined structure.
As a result, every data science project begins with the same tasks: gather the data, view the data, clean the data, correct or change the layout of the data to make it tidy, handle missing values and outliers from the data, model the data, and evaluate the data.
With R, you can do everything from collecting your data (from the web or a database) to cleaning it, transforming it, visualizing it, modelling it, and running statistical tests on it.
Reading data from CSV files
CSV formats are best used to represent sets or sequences of records in which each record has an identical list of fields. This corresponds to a single relation in a relational database, or to data (though not calculations) in a typical spreadsheet.
Getting ready
If you have not already downloaded the files for this chapter, do it now and ensure that the auto-mpg.csv file is in your R working directory.
How to do it...
Reading data from .csv files can be done using the following commands:
- Read the data from auto-mpg.csv, which includes a header row:
> auto <- read.csv("auto-mpg.csv", header=TRUE, sep = ",")
- Verify the results:
> names(auto)
How it works...
The read.csv() function creates a data frame from the data in the .csv file. If we pass header=TRUE, then the function uses the very first row to name the variables in the resulting data frame:
> names(auto)
[1] "No" "mpg" "cylinders"
[4] "displacement" "horsepower" "weight"
[7] "acceleration" "model_year" "car_name"
The header and sep parameters allow us to specify whether the .csv file has headers and the character used in the file to separate fields. The header=TRUE and sep="," parameters are the defaults for the read.csv() function; we can omit these in the code example.
There's more...
The read.csv() function is a specialized form of read.table(). The latter uses whitespace as the default field separator. We will discuss a few important optional arguments to these functions.
Handling different column delimiters
In regions where a comma is used as the decimal separator, the .csv files use ";" as the field delimiter. While dealing with such data files, use read.csv2() to load data into R.
Alternatively, you can use the read.csv("<file name>", sep=";", dec=",") command.
Use sep="t" for tab-delimited files.
Handling column headers/variable names
If your data file does not have column headers, set header=FALSE.
The auto-mpg-noheader.csv file does not include a header row. The first command in the following snippet reads this file. In this case, R assigns default variable names V1, V2, and so on.
> auto <- read.csv("auto-mpg-noheader.csv", header=FALSE)
> head(auto,2)
V1 V2 V3 V4 V5 V6 V7 V8 V9
1 1 28 4 140 90 2264 15.5 71 chevrolet vega 2300
2 2 19 3 70 97 2330 13.5 72 mazda rx2 coupe
If your file does not have a header row, and you omit the header=FALSE optional argument, the read.csv() function uses the first row for variable names and ends up constructing variable names by adding X to the actual data values in the first row. Note the meaningless variable names in the following fragment:
> auto <- read.csv("auto-mpg-noheader.csv")
> head(auto,2)
X1 X28 X4 X140 X90 X2264 X15.5 X71 chevrolet.vega.2300
1 2 19 3 70 97 2330 13.5 72 mazda rx2 coupe
2 3 36 4 107 75 2205 14.5 82 honda accord
We can use the optional col.names argument to specify the column names. If col.names is given explicitly, the names in the header row are ignored, even if header=TRUE is specified:
> auto <- read.csv("auto-mpg-noheader.csv", header=FALSE, col.names = c("No", "mpg", "cyl", "dis","hp", "wt", "acc", "year", "car_name"))
> head(auto,2)
No mpg cyl dis hp wt acc year car_name
1 1 28 4 140 90 2264 15.5 71 chevrolet vega 2300
2 2 19 3 70 97 2330 13.5 72 mazda rx2 coupe
Handling missing values
When reading data from text files, R treats blanks in numerical variables as NA (signifying missing data). By default, it reads blanks in categorical attributes just as blanks and not as NA. To treat blanks as NA for categorical and character variables, set na.strings="":
> auto <- read.csv("auto-mpg.csv", na.strings="")
If the data file uses a specified string (such as "N/A" or "NA" for example) to indicate the missing values, you can specify that string as the na.strings argument, as in na.strings= "N/A" or na.strings = "NA".
Reading strings as characters and not as factors
By default, R treats strings as factors (categorical variables). In some situations, you may want to leave them as character strings. Use stringsAsFactors=FALSE to achieve this:
> auto <- read.csv("auto-mpg.csv",stringsAsFactors=FALSE)
However, to selectively treat variables as characters, you can load the file with the defaults (that is, read all strings as factors) and then use as.character() to convert the requisite factor variables to characters.
Reading data directly from a website
If the data file is available on the web, you can load it directly into R, instead of downloading and saving it locally before loading it into R:
> dat <- read.csv("")
Reading XML data
You may sometimes need to extract data from websites. Many providers also supply data in XML and JSON formats. In this recipe, we learn about reading XML data.
Getting ready
Make sure you have downloaded the files for this chapters and the files cd_catalog.xml and WorldPopulation-wiki.htm are in working directory of R. If the XML package is not already installed in your R environment, install the package now, as follows:
> install.packages("XML")
How to do it...
XML data can be read by following these steps:
- Load the library and initialize:
> library(XML)
> url <- "cd_catalog.xml"
- Parse the XML file and get the root node:
> xmldoc <- xmlParse(url)
> rootNode <- xmlRoot(xmldoc)
> rootNode[1]
- Extract the XML data:
> data <- xmlSApply(rootNode,function(x) xmlSApply(x, xmlValue))
- Convert the extracted data into a data frame:
> cd.catalog <- data.frame(t(data),row.names=NULL)
- Verify the results:
> cd.catalog[1:2,]
How it works...
The xmlParse function returns an object of the XMLInternalDocument class, which is a C-level internal data structure.
The xmlRoot() function gets access to the root node and its elements. Let us check the first element of the root node:
> rootNode[1]
$CD
<CD>
<TITLE>Empire Burlesque</TITLE>
<ARTIST>Bob Dylan</ARTIST>
<COUNTRY>USA</COUNTRY>
<COMPANY>Columbia</COMPANY>
<PRICE>10.90</PRICE>
<YEAR>1985</YEAR>
</CD>
attr(,"class")
[1] "XMLInternalNodeList" "XMLNodeList"
To extract data from the root node, we use the xmlSApply() function iteratively over all the children of the root node. The xmlSApply function returns a matrix.
To convert the preceding matrix into a data frame, we transpose the matrix using the t() function and then extract the first two rows from the cd.catalog data frame:
> cd.catalog[1:2,]
TITLE ARTIST COUNTRY COMPANY PRICE YEAR
1 Empire Burlesque Bob Dylan USA Columbia 10.90 1985
2 Hide your heart Bonnie Tyler UK CBS Records 9.90 1988
There's more...
XML data can be deeply nested and hence can become complex to extract. Knowledge of XPath is helpful to access specific XML tags. R provides several functions, such as xpathSApply and getNodeSet, to locate specific elements.
Extracting HTML table data from a web page
Though it is possible to treat HTML data as a specialized form of XML, R provides specific functions to extract data from HTML tables, as follows:
> url <- "WorldPopulation-wiki.htm"
> tables <- readHTMLTable(url)
> world.pop <- tables[[6]]
The readHTMLTable() function parses the web page and returns a list of all the tables that are found on the page. For tables that have an id attribute, the function uses the id attribute as the name of that list element.
We are interested in extracting the "10 most populous countries", which is the fifth table, so we use tables[[6]].
Extracting a single HTML table from a web page
A single table can be extracted using the following command:
> table <- readHTMLTable(url,which=5)
Specify which to get data from a specific table. R returns a data frame.
Reading JSON data
Several RESTful web services return data in JSON format, in some ways simpler and more efficient than XML. This recipe shows you how to read JSON data.
Getting ready
R.
How to do it...
Once the files are ready, load the jsonlite package and read the files as follows:
- Load the library:
> library(jsonlite)
- Load the JSON data from the files:
> dat.1 <- fromJSON("students.json")
> dat.2 <- fromJSON("student-courses.json")
- Load the JSON document from the web:
> url <- ""
> jsonDoc <- fromJSON(url)
- Extract the data into data frames:
> dat <- jsonDoc$list$resources$resource$fields
> dat.1 <- jsonDoc$list$resources$resource$fields
> dat.2 <- jsonDoc$list$resources$resource$fields
- Verify the results:
> dat[1:2,]
> dat.1[1:3,]
> dat.2[,c(1,2,4:5)]
How it works...
The jsonlite package provides two key functions: fromJSON and toJSON.
The fromJSON function can load data either directly from a file or from a web page, as the preceding steps 2 and 3 show. If you get errors in downloading content directly from the web, install and load the httr package.
Depending on the structure of the JSON document, loading the data can vary in complexity.
If given a URL, the fromJSON function returns a list object. In the preceding list, in step 4, we see how to extract the enclosed data frame.
Reading data from fixed-width formatted files
In fixed-width formatted files, columns have fixed widths; if a data element does not use up the entire allotted column width, then the element is padded with spaces to make up the specified width. To read fixed-width text files, specify the columns either by column widths or by starting positions.
Getting ready
Download the files for this chapter and store the student-fwf.txt file in your R working directory.
How to do it...
Read the fixed-width formatted file as follows:
> student <- read.fwf("student-fwf.txt", widths=c(4,15,20,15,4), col.names=c("id","name","email","major","year"))
How it works...
In the student-fwf.txt file, the first column occupies 4 character positions, the second 15, and so on. The c(4,15,20,15,4) expression specifies the widths of the 5 columns in the data file.
We can use the optional col.names argument to supply our own variable names.
There's more...
The read.fwf() function has several optional arguments that come in handy. We discuss a few of these, as follows:
Files with headers
Files with headers use the following command:
> student <- read.fwf("student-fwf-header.txt", widths=c(4,15,20,15,4), header=TRUE, sep="t",skip=2)
If header=TRUE, the first row of the file is interpreted as having the column headers. Column headers, if present, need to be separated by the specified sep argument. The sep argument only applies to the header row.
The skip argument denotes the number of lines to skip; in this recipe, the first two lines are skipped.
Excluding columns from data
To exclude a column, make the column width negative. Thus, to exclude the email column, we will specify its width as -20 and also remove the column name from the col.names vector, as follows:
> student <- read.fwf("student-fwf.txt",widths=c(4,15,-20,15,4), col.names=c("id","name","major","year"))
Reading data from R files and R libraries
During data analysis, you will create several R objects. You can save these in the native R data format and retrieve them later as needed.
Getting ready
First, create and save the R objects interactively, as shown in the following code. Make sure you have write access to the R working directory.
> customer <- c("John", "Peter", "Jane")
> orderdate <- as.Date(c('2014-10-1','2014-1-2','2014-7-6'))
> orderamount <- c(280, 100.50, 40.25)
> order <- data.frame(customer,orderdate,orderamount)
> names <- c("John", "Joan")
> save(order, names, file="test.Rdata")
> saveRDS(order,file="order.rds")
> remove(order)
After saving the preceding code, the remove() function deletes the object from the current session.
How to do it...
To be able to read data from R files and libraries, follow these steps:
- Load data from the R data files into memory:
> load("test.Rdata")
> ord <- readRDS("order.rds")
- The datasets package is loaded in the R environment by default and contains the iris and cars datasets. To load these datasets data into memory, use the following code:
> data(iris)
> data(list(cars,iris))
The first command loads only the iris dataset, and the second loads both the cars and iris datasets.
How it works...
The save() function saves the serialized version of the objects supplied as arguments along with the object name. The subsequent load() function restores the saved objects, with the same object names that they were saved with, to the global environment by default. If there are existing objects with the same names in that environment, they will be replaced without any warnings.
The saveRDS() function saves only one object. It saves the serialized version of the object and not the object name. Hence, with the readRDS() function, the saved object can be restored into a variable with a different name from when it was saved.
There's more...
The preceding recipe has shown you how to read saved R objects. We see more options in this section.
Saving all objects in a session
The following command can be used to save all objects:
> save.image(file = "all.RData")
Saving objects selectively in a session
To save objects selectively, use the following commands:
> odd <- c(1,3,5,7)
> even <- c(2,4,6,8)
> save(list=c("odd","even"),file="OddEven.Rdata")
The list argument specifies a character vector containing the names of the objects to be saved. Subsequently, loading data from the OddEven.Rdata file creates both odd and even objects. The saveRDS() function can save only one object at a time.
Attaching/detaching R data files to an environment
While
Listing all datasets in loaded packages
All the loaded packages can be listed using the following command:
> data()
Removing cases with missing values
Datasets come with varying amounts of missing data. When we have abundant data, we sometimes (not always) want to eliminate the cases that have missing values for one or more variables. This recipe applies when we want to eliminate cases that have any missing values, as well as when we want to selectively eliminate cases that have missing values for a specific variable alone.
Getting ready
Download the missing-data.csv file from the code files for this chapter to your R working directory. Read the data from the missing-data.csv file, while taking care to identify the string used in the input file for missing values. In our file, missing values are shown with empty strings:
> dat <- read.csv("missing-data.csv", na.strings="")
How to do it...
To get a data frame that has only the cases with no missing values for any variable, use the na.omit() function:
> dat.cleaned <- na.omit(dat)
Now dat.cleaned contains only those cases from dat that have no missing values in any of the variables.
How it works...
The na.omit() function internally uses the is.na() function, that allows us to find whether its argument is NA. When applied to a single value, it returns a Boolean value. When applied to a collection, it returns a vector:
> is.na(dat[4,2])
[1] TRUE
> is.na(dat$Income)
[1] FALSE FALSE FALSE FALSE FALSE TRUE FALSE FALSE FALSE
[10] FALSE FALSE FALSE TRUE FALSE FALSE FALSE FALSE FALSE
[19] FALSE FALSE FALSE FALSE FALSE FALSE FALSE FALSE FALSE
There's more...
You will sometimes need to do more than just eliminate the cases with any missing values. We discuss some options in this section.
Eliminating cases with NA for selected variables
We might sometimes want to selectively eliminate cases that have NA only for a specific variable. The example data frame has two missing values for Income. To get a data frame with only these two cases removed, use:
> dat.income.cleaned <- dat[!is.na(dat$Income),]
> nrow(dat.income.cleaned)
[1] 25
Finding cases that have no missing values
The complete.cases() function takes a data frame or table as its argument and returns a Boolean vector with TRUE for rows that have no missing values, and FALSE otherwise:
> complete.cases(dat)
[1] TRUE TRUE TRUE FALSE TRUE FALSE TRUE TRUE TRUE
[10] TRUE TRUE TRUE FALSE TRUE TRUE TRUE FALSE TRUE
[19] TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE
Rows 4, 6, 13, and 17 have at least one missing value. Instead of using the na.omit() function, we can do the following as well:
> dat.cleaned <- dat[complete.cases(dat),]
> nrow(dat.cleaned)
[1] 23
Converting specific values to NA
Sometimes, we might know that a specific value in a data frame actually means that the data was not available. For example, in the dat data frame, a value of 0 for Income probably means that the data is missing. We can convert these to NA by a simple assignment:
> dat$Income[dat$Income==0] <- NA
Excluding NA values from computations
Many R functions return NA when some parts of the data they work on are NA. For example, computing the mean or sd on a vector with at least one NA value returns NA as the result. To remove NA from consideration, use the na.rm parameter:
> mean(dat$Income)
[1] NA
> mean(dat$Income, na.rm = TRUE)
[1] 65763.64
Replacing missing values with the mean
When you disregard cases with any missing variables, you lose useful information that the non-missing values in that case convey. You may sometimes want to impute reasonable values (those that will not skew the results of analysis very much) for the missing values.
Getting ready
Download the missing-data.csv file and store it in your R environment's working directory.
How to do it...
Read data and replace missing values:
> dat <- read.csv("missing-data.csv", na.strings = "")
> dat$Income.imp.mean <- ifelse(is.na(dat$Income), mean(dat$Income, na.rm=TRUE), dat$Income)
After this, all the NA values for Income will be the mean value prior to imputation.
How it works...
The preceding ifelse() function returns the imputed mean value if its first argument is NA. Otherwise, it returns the first argument.
There's more...
You cannot impute the mean when a categorical variable has missing values, so you need a different approach. Even for numeric variables, we might sometimes not want to impute the mean for missing values. We discuss an often-used approach here.
Imputing random values sampled from non-missing values
If you want to impute random values sampled from the non-missing values of the variable, you can use the following two functions:
rand.impute <- function(a) {
missing <- is.na(a)
n.missing <- sum(missing)
a.obs <- a[!missing]
imputed <- a
imputed[missing] <- sample (a.obs, n.missing, replace=TRUE)
return (imputed)
}
random.impute.data.frame <- function(dat, cols) {
nms <- names(dat)
for(col in cols) {
name <- paste(nms[col],".imputed", sep = "")
dat[name] <- rand.impute(dat[,col])
}
dat
}
With these two functions in place, you can use the following to impute random values for both Income and Phone_type:
> dat <- read.csv("missing-data.csv", na.strings="")
> random.impute.data.frame(dat, c(1,2))
Removing duplicate cases
We sometimes end up with duplicate cases in our datasets and want to retain only one among them.
Getting ready
Create a sample data frame:
> salary <- c(20000, 30000, 25000, 40000, 30000, 34000, 30000)
> family.size <- c(4,3,2,2,3,4,3)
> car <- c("Luxury", "Compact", "Midsize", "Luxury", "Compact", "Compact", "Compact")
> prospect <- data.frame(salary, family.size, car)
How to do it...
The unique() function can do the job. It takes a vector or data frame as an argument and returns an object of the same type as its argument, but with duplicates removed.
Remove duplicates to get unique values:
> prospect.cleaned <- unique(prospect)
> nrow(prospect)
[1] 7
> nrow(prospect.cleaned)
[1] 5
How it works...
The unique() function takes a vector or data frame as an argument and returns a similar object with the duplicate eliminated. It returns the non-duplicated cases as is. For repeated cases, the unique() function includes one copy in the returned result.
There's more...
Sometimes we just want to identify the duplicated values without necessarily removing them.
Identifying duplicates without deleting them
For this, use the duplicated() function:
> duplicated(prospect)
[1] FALSE FALSE FALSE FALSE TRUE FALSE TRUE
From the data, we know that cases 2, 5, and 7 are duplicates. Note that only cases 5 and 7 are shown as duplicates. In the first occurrence, case 2 is not flagged as a duplicate.
To list the duplicate cases, use the following code:
> prospect[duplicated(prospect), ]
salary family.size car
5 30000 3 Compact
7 30000 3 Compact
Rescaling a variable to specified min-max range
Distance computations play a big role in many data analytics techniques. We know that variables with higher values tend to dominate distance computations and you may want to rescale the values to be in the range of 0 - 1.
Getting ready
Install the scales package and read the data-conversion.csv file from the book's data for this chapter into your R environment's working directory:
> install.packages("scales")
> library(scales)
> students <- read.csv("data-conversion.csv")
How to do it...
To rescale the Income variable to the range [0,1], use the following code snippet:
> students$Income.rescaled <- rescale(students$Income)
How it works...
By default, the rescale() function makes the lowest value(s) zero and the highest value(s) one. It rescales all the other values proportionately. The following two expressions provide identical results:
> rescale(students$Income)
> (students$Income - min(students$Income)) / (max(students$Income) - min(students$Income))
To rescale a different range than [0,1], use the to argument. The following snippet rescales students$Income to the range (0,100):
> rescale(students$Income, to = c(1, 100))
There's more...
When using distance-based techniques, you may need to rescale several variables. You may find it tedious to scale one variable at a time.
Rescaling many variables at once
Use the following function to rescale variables:
rescale.many <- function(dat, column.nos) {
nms <- names(dat)
for(col in column.nos) {
name <- paste(nms[col],".rescaled", sep = "")
dat[name] <- rescale(dat[,col])
}
cat(paste("Rescaled ", length(column.nos), " variable(s)n"))
dat
}
With the preceding function defined, we can do the following to rescale the first and fourth variables in the data frame:
> rescale.many(students, c(1,4))
See also
- The Normalizing or standardizing data in a data frame recipe in this chapter.
Normalizing or standardizing data in a data frame
Distance computations play a big role in many data analytics techniques. We know that variables with higher values tend to dominate distance computations and you may want to use the standardized (or z) values.
Getting ready
Download the BostonHousing.csv data file and store it in your R environment's working directory. Then read the data:
> housing <- read.csv("BostonHousing.csv")
How to do it...
To standardize all the variables in a data frame containing only numeric variables, use:
> housing.z <- scale(housing)
You can only use the scale() function on data frames that contain all numeric variables. Otherwise, you will get an error.
How it works...
When invoked in the preceding example, the scale() function computes the standard z score for each value (ignoring NAs) of each variable. That is, from each value it subtracts the mean and divides the result by the standard deviation of the associated variable.
The scale() function takes two optional arguments, center and scale, whose default values are TRUE. The following table shows the effect of these arguments:
There's more...
When using distance-based techniques, you may need to rescale several variables. You may find it tedious to standardize one variable at a time.
Standardizing several variables simultaneously
If you have a data frame with some numeric and some non-numeric variables, or want to standardize only some of the variables in a fully numeric data frame, then you can either handle each variable separately, which would be cumbersome, or use a function such as the following to handle a subset of variables:
scale.many <- function(dat, column.nos) {
nms <- names(dat)
for(col in column.nos) {
name <- paste(nms[col],".z", sep = "")
dat[name] <- scale(dat[,col])
}
cat(paste("Scaled ", length(column.nos), " variable(s)n"))
dat
}
With this function, you can now do things like:
> housing <- read.csv("BostonHousing.csv")
> housing <- scale.many(housing, c(1,3,5:7))
This will add the z values for variables 1, 3, 5, 6, and 7, with .z appended to the original column names:
> names(housing)
[1] "CRIM" "ZN" "INDUS" "CHAS" "NOX" "RM"
[7] "AGE" "DIS" "RAD" "TAX" "PTRATIO" "B"
[13] "LSTAT" "MEDV" "CRIM.z" "INDUS.z" "NOX.z" "RM.z"
[19] "AGE.z"
See also
Rescaling a variable to [0,1] recipe in this chapter.
Binning numerical data
Sometimes, we need to convert numerical data to categorical data or a factor. For example, Naive Bayes classification requires all variables (independent and dependent) to be categorical. In other situations, we may want to apply a classification method to a problem where the dependent variable is numeric but needs to be categorical.
Getting ready
From the code files for this chapter, store the data-conversion.csv file in the working directory of your R environment. Then read the data:
> students <- read.csv("data-conversion.csv")
How to do it...
Income is a numeric variable, and you may want to create a categorical variable from it by creating bins. Suppose you want to label incomes of $10,000 or below as Low, incomes between $10,000 and $31,000 as Medium, and the rest as High. We can do the following:
- Create a vector of break points:
> b <- c(-Inf, 10000, 31000, Inf)
- Create a vector of names for break points:
> names <- c("Low", "Medium", "High")
- Cut the vector using the break points:
> students$Income.cat <- cut(students$Income, breaks = b, labels = names)
> students
Age State Gender Height Income Income.cat
1 23 NJ F 61 5000 Low
2 13 NY M 55 1000 Low
3 36 NJ M 66 3000 Low
4 31 VA F 64 4000 Low
5 58 NY F 70 30000 Medium
6 29 TX F 63 10000 Low
7 39 NJ M 67 50000 High
8 50 VA M 70 55000 High
9 23 TX F 61 2000 Low
10 36 VA M 66 20000 Medium
How it works...
The cut() function uses the ranges implied by the breaks argument to infer the bins, and names them according to the strings provided in the labels argument. In our example, the function places incomes less than or equal to 10,000 in the first bin, incomes greater than 10,000 and less than or equal to 31,000 in the second bin, and incomes greater than 31,000 in the third bin. In other words, the first number in the interval is not included but the second one is. The number of bins will be one less than the number of elements in breaks. The strings in names become the factor levels of the bins.
If we leave out names, cut() uses the numbers in the second argument to construct interval names, as you can see here:
> b <- c(-Inf, 10000, 31000, Inf)
> students$Income.cat1 <- cut(students$Income, breaks = b)
> students
Age State Gender Height Income Income.cat Income.cat1
1 23 NJ F 61 5000 Low (-Inf,1e+04]
2 13 NY M 55 1000 Low (-Inf,1e+04]
3 36 NJ M 66 3000 Low (-Inf,1e+04]
4 31 VA F 64 4000 Low (-Inf,1e+04]
5 58 NY F 70 30000 Medium (1e+04,3.1e+04]
6 29 TX F 63 10000 Low (-Inf,1e+04]
7 39 NJ M 67 50000 High (3.1e+04, Inf]
8 50 VA M 70 55000 High (3.1e+04, Inf]
9 23 TX F 61 2000 Low (-Inf,1e+04]
10 36 VA M 66 20000 Medium (1e+04,3.1e+04]
There's more...
You might not always be in a position to identify the breaks manually and may instead want to rely on R to do this automatically.
Creating a specified number of intervals automatically
Rather than determining the breaks and hence the intervals manually, as mentioned earlier, we can specify the number of bins we want, say n, and let the cut() function handle the rest automatically. In this case, cut() creates n intervals of approximately equal width, as follows:
> students$Income.cat2 <- cut(students$Income, breaks = 4, labels = c("Level1", "Level2", "Level3","Level4"))
Creating dummies for categorical variables
In situations where we have categorical variables (factors) but need to use them in analytical methods that require numbers (for example, K nearest neighbors (KNN), Linear Regression), we need to create dummy variables.
Getting ready
Read the data-conversion.csv file and store it in the working directory of your R environment. Install the dummies package. Then read the data:
> install.packages("dummies")
> library(dummies)
> students <- read.csv("data-conversion.csv")
How to do it...
Create dummies for all factors in the data frame:
> students.new <- dummy.data.frame(students, sep = ".")
> names(students.new)
[1] "Age" "State.NJ" "State.NY" "State.TX" "State.VA"
[6] "Gender.F" "Gender.M" "Height" "Income"
The students.new data frame now contains all the original variables and the newly added dummy variables. The dummy.data.frame() function has created dummy variables for all four levels of State and two levels of Gender factors. However, we will generally omit one of the dummy variables for State and one for Gender when we use machine learning techniques.
We can use the optional argument all = FALSE to specify that the resulting data frame should contain only the generated dummy variables and none of the original variables.
How it works...
The dummy.data.frame() function creates dummies for all the factors in the data frame supplied. Internally, it uses another dummy() function which creates dummy variables for a single factor. The dummy() function creates one new variable for every level of the factor for which we are creating dummies. It appends the variable name with the factor level name to generate names for the dummy variables. We can use the sep argument to specify the character that separates them; an empty string is the default:
> dummy(students$State, sep = ".")
State.NJ State.NY State.TX State.VA
[1,] 1 0 0 0
[2,] 0 1 0 0
[3,] 1 0 0 0
[4,] 0 0 0 1
[5,] 0 1 0 0
[6,] 0 0 1 0
[7,] 1 0 0 0
[8,] 0 0 0 1
[9,] 0 0 1 0
[10,] 0 0 0 1
There's more...
In situations where a data frame has several factors, and you plan on using only a subset of them, you create dummies only for the chosen subset.
Choosing which variables to create dummies for
To create a dummy only for one variable or a subset of variables, we can use the names argument to specify the column names of the variables we want dummies for:
> students.new1 <- dummy.data.frame(students, names = c("State","Gender") , sep = ".")
Handling missing data
In most real-world problems, data is likely to be incomplete because of incorrect data entry, faulty equipment, or improperly coded data. In R, missing values are represented by the symbol NA (not available) and are considered to be the first obstacle in predictive modeling. So, it's always a good idea to check for missing data in a dataset before proceeding for further predictive analysis. This recipe shows you how to handle missing data.
Getting ready
R provides three simple ways to handle missing values:
- Deleting the observations.
- Deleting the variables.
- Replacing the values with mean, median, or mode.
Install the package in your R environment as follows:
> install.packages("Hmisc")
If you have not already downloaded the files for this chapter, do it now and ensure that the housing-with-missing-value.csv file is in your R working directory.
How to do it...
Once the files are ready, load the Hmisc package and read the files as follows:
- Load the CSV data from the files:
> housing.dat <- read.csv("housing-with-missing-value.csv",header = TRUE, stringsAsFactors = FALSE)
- Check summary of the dataset:
> summary(housing.dat)
The output would be as follows:
- Delete the missing observations from the dataset, removing all NAs with list-wise deletion:
> housing.dat.1 <- na.omit(housing.dat)
Remove NAs from certain columns:
> drop_na <- c("rad")
> housing.dat.2 <-housing.dat [complete.cases(housing.dat [ , !(names(housing.dat)) %in% drop_na]),]
- Finally, verify the dataset with summary statistics:
> summary(housing.dat.1$rad)
Min. 1st Qu. Median Mean 3rd Qu. Max.
1.000 4.000 5.000 9.599 24.000 24.000
> summary(housing.dat.1$ptratio)
Min. 1st Qu. Median Mean 3rd Qu. Max.
12.60 17.40 19.10 18.47 20.20 22.00
> summary(housing.dat.2$rad)
Min. 1st Qu. Median Mean 3rd Qu. Max. NA's
1.000 4.000 5.000 9.599 24.000 24.000 35
> summary(housing.dat.2$ptratio)
Min. 1st Qu. Median Mean 3rd Qu. Max.
12.60 17.40 19.10 18.47 20.20 22.00
- Delete the variables that have the most missing observations:
# Deleting a single column containing many NAs
> housing.dat.3 <- housing.dat$rad <- NULL
#Deleting multiple columns containing NAs:
> drops <- c("ptratio","rad")
>housing.dat.4 <- housing.dat[ , !(names(housing.dat) %in% drops)]
Finally, verify the dataset with summary statistics:
> summary(housing.dat.4)
- Load the library:
> library(Hmisc)
- Replace the missing values with mean, median, or mode:
#replace with mean
> housing.dat$ptratio <- impute(housing.dat$ptratio, mean)
> housing.dat$rad <- impute(housing.dat$rad, mean)
#replace with median
> housing.dat$ptratio <- impute(housing.dat$ptratio, median)
> housing.dat$rad <- impute(housing.dat$rad, median)
#replace with mode/constant value
> housing.dat$ptratio <- impute(housing.dat$ptratio, 18)
> housing.dat$rad <- impute(housing.dat$rad, 6)
Finally, verify the dataset with summary statistics:
> summary(housing.dat)
How it works...
When you have large numbers of observations in your dataset and all the classes to be predicted are sufficiently represented by the data points, then deleting missing observations would not introduce bias or disproportionality of output classes.
In the housing.dat dataset, we saw from the summary statistics that the dataset has two columns, ptratio and rad, with missing values.
The na.omit() function lets you remove all the missing values from all the columns of your dataset, whereas the complete.cases() function lets you remove the missing values from some particular column/columns.
Sometimes, particular variable/variables might have more missing values than the rest of the variables in the dataset. Then it is better to remove that variable unless it is a really important predictor that makes a lot of business sense. Assigning NULL to a variable is an easy way of removing it from the dataset.
In both, the given way of handling missing values through the deletion approach reduces the total number of observations (or rows) from the dataset. Instead of removing missing observations or removing a variable with many missing values, replacing the missing values with the mean, median, or mode is often a crude way of treating the missing values. Depending on the context, such as if the variation is low or if the variable has low leverage over the response/target, such a naive approximation is acceptable and could possibly give satisfactory results. The impute() function in the Hmisc library provides an easy way to replace the missing value with the mean, median, or mode (constant).
There's more...
Sometime it is better to understand the missing pattern in the dataset through visualization before taking further decision about elimination or imputation of the missing values.
Understanding missing data pattern
Let us use the md.pattern() function from the mice package to get a better understanding of the pattern of missing data.
> library(mice)
> md.pattern(housing.dat)
We can notice from the output above that 466 samples are complete, 40 samples miss only the ptratio value.
Next we will visualize the housing data to understand missing information using aggr_plot method from VIM package:
> library(VIM)
> aggr_plot <- aggr(housing.dat, col=c('blue','red'), numbers=TRUE, sortVars=TRUE, labels=names(housing.dat), cex.axis=.7, gap=3, ylab=c("Histogram of missing data","Pattern"))
We can understand from the plot that almost 92.1% of the samples are complete and only 7.9% are missing information from the ptratio values.
Correcting data
In practice, raw data is rarely tidy, and is much harder to work with as a result. It is often said that 80 percent of data analysis is spent on the process of cleaning and correcting the data.
In this recipe, you will learn the best way to correctly layout your data to serve two major purposes:
- Making data suitable for software processing, whether that be mathematical functions, visualization, and others
- Revealing information and insights
Getting ready
Download the files for this chapter and store the USArrests.csv file in your R working directory. You should also install the tidyr package using the following command.
> install.packages("tidyr")
> library(tidyr)
> crimeData <- read.csv("USArrests.csv",stringsAsFactors = FALSE)
How to do it...
Follow these steps to correct the data from your dataset.
- View some records of the dataset:
> View(crimeData)
- Add the column name state in the dataset:
> crimeData <- cbind(state = rownames(crimeData), crimeData)
- Gather all the variables between Murder and UrbanPop:
> crimeData.1 <- gather(crimeData,
key = "crime_type",
value = "arrest_estimate",
Murder:UrbanPop)
> crimeData.1
- Gather all the columns except the column state:
> crimeData.2 <- gather(crimeData,
key = "crime_type",
value = "arrest_estimate",
-state)
> crimeData.2
- Gather only the Murder and Assault columns:
> crimeData.3 <- gather(crimeData,
key = "crime_type",
value = "arrest_estimate",
Murder, Assault)
> crimeData.3
- Spread crimeData.2 to turn a pair of key:value (crime_typ:arrest_estimate) columns into a set of tidy columns
> crimeData.4 <- spread(crimeData.2,
key = "crime_type",
value = "arrest_estimate"
)
> crimeData.4
How it works...
Correct data format is crucial for facilitating the tasks of data analysis, including data manipulation, modeling, and visualization. The tidy data arranges values so that the relationships in the data parallel the structure of the data frame. Every tidy dataset is based on two basic principles:
- Each variable is saved in its own column
- Each observation is saved in its own row
In the crimeData dataframe, the row names were states, hence we used the function cbind() to add a column named state in the dataframe. The function gather() collapses multiple columns into key-value pairs. It makes wide data longer. The gather() function basically takes four arguments, data (dataframe), key (column name representing new variable), value (column name representing variable values), and names of the columns to gather (or not gather).
In the crimeData.2 data, all column names (except state) were collapsed into a single key column crime_type and their values were put into a value column arrest_estimate.
And, in the crimeData.3 data, the two columns Murder and Assault were collapsed and the remaining columns (state, UrbanPop, and Rape) were
duplicated.
The function spread() does the reverse of gather(). It takes two columns (key and value) and spreads them into multiple columns. It makes long data wider. The spread() function takes three arguments in general, data (dataframe), key (column values to convert to multiple columns), and value (single column value to convert to multiple columns' values).
There's more...
Beside the spread() and gather() functions, there are two more important functions in the tidyr package that help to make data tidy.
Combining multiple columns to single columns
The unite() function takes multiple columns and pastes them together into one column:
> crimeData.5 <- unite(crimeData,
col = "Murder_Assault",
Murder, Assault,
sep = "_")
> crimeData.5
We combine the columns Murder and Assault from the crimeData
data-frame to generate a new column Murder_Assault, having the values separated by _.
Splitting single column to multiple columns
The separate() function is the reverse of unite(). It takes values inside a single character column and separates them into multiple columns:
> crimeData.6 <- separate_(crimeData.5,
col = "Murder_Assault",
into = c("Murder", "Assault"),
sep = "_")
>crimeData.6
Imputing data
Missing values are considered to be the first obstacle in data analysis and predictive modeling. In most statistical analysis methods, list-wise deletion is the default method used to impute missing values, as shown in the earlier recipe. However, these methods are not quite good enough, since deletion could lead to information loss and replacement with simple mean or median, which doesn't take into account the uncertainty in missing values.
Hence, this recipe will show you the multivariate imputation techniques to handle missing values using prediction.
Getting ready
Make sure that the housing-with-missing-value.csv file from the code files of this chapter is in your R working directory.
You should also install the mice package using the following command:
> install.packages("mice")
> library(mice)
> housingData <- read.csv("housing-with-missing-value.csv",header = TRUE, stringsAsFactors = FALSE)
How to do it...
Follow these steps to impute data:
- Perform multivariate imputation:
#imputing only two columns having missing values
> columns=c("ptratio","rad")
> imputed_Data <- mice(housingData[,names(housingData) %in% columns], m=5, maxit = 50, method = 'pmm', seed = 500)
>summary(imputed_Data)
- Generate complete data:
> completeData <- complete(imputed_Data)
- Replace the imputed column values with the housing.csv dataset:
> housingData$ptratio <- completeData$ptratio
> housingData$rad <- completeData$rad
- Check for missing values:
> anyNA(housingData)
How it works...
As we already know from our earlier recipe, the housing.csv dataset contains two columns, ptratio and rad, with missing values.
The mice library in R uses a predictive approach and assumes that the missing data is Missing at Random (MAR), and creates multivariate imputations via chained equations to take care of uncertainty in the missing values. It implements the imputation in just two steps: using mice() to build the model and complete() to generate the completed data.
The mice() function takes the following parameters:
- m: It refers to the number of imputed datasets it creates internally. Default is five.
- maxit: It refers to the number of iterations taken to impute the missing values.
- method: It refers to the method used in imputation. The default imputation method (when no argument is specified) depends on the measurement level of the target column and is specified by the defaultMethod argument, where defaultMethod = c("pmm", "logreg", "polyreg", "polr").
- logreg: Logistic regression (factor column, two levels).
- polyreg: Polytomous logistic regression (factor column, greater than or equal to two levels).
- polr: Proportional odds model (ordered column, greater than or equal to two levels).
We have used predictive mean matching (pmm) for this recipe to impute the missing values in the dataset.
The anyNA() function returns a Boolean value to indicate the presence or absence of missing values (NA) in the dataset.
There's more...
Previously, we used the impute() function from the Hmisc library to simply impute the missing value using defined statistical methods (mean, median, and mode). However, Hmisc also has the aregImpute() function that allows mean imputation using additive regression, bootstrapping, and predictive mean matching:
> impute_arg <- aregImpute(~ ptratio + rad , data = housingData, n.impute = 5)
> impute_arg
argImpute() automatically identifies the variable type and treats it accordingly, and the n.impute parameter indicates the number of multiple imputations, where five is recommended.
The output of impute_arg shows R² values for predicted missing values. The higher the value, the better the values predicted.
Check imputed variable values using the following command:
> impute_arg$imputed$rad
Detecting outliers
Outliers in data can distort predictions and affect the accuracy, if you don't detect and handle them appropriately, especially in the data preprocessing stage.
So, identifying the extreme values is important, as it can drastically introduce bias in the analytic pipeline and affect predictions. In this recipe, we will discuss the ways to detect outliers and how to handle them.
Getting ready
Download the files for this chapter and store the ozone.csv file in your R working directory. Read the file using the read.csv() command and save it in a variable:
> ozoneData <- read.csv("ozone.csv", stringsAsFactors=FALSE)
How to do it...
Perform the following steps to detect outliers in the dataset:
- Detect outliers in the univariate continuous variable:
>outlier_values <- boxplot.stats(ozoneData$pressure_height)$out
>boxplot(ozoneData$pressure_height, main="Pressure Height", boxwex=0.1)
>mtext(paste("Outliers: ", paste(outlier_values, collapse=", ")), cex=0.6)
The output would be the following screenshot:
- Detect outliers in bivariate categorical variables:
> boxplot(ozone_reading ~ Month, data=ozoneData, main="Ozone reading across months")
The output would be the following screenshot:
How it works...
The most commonly used method to detect outliers is visualization of the data, through boxplot, histogram, or scatterplot.
The boxplot.stats()$out function fetches the values of data points that lie beyond the extremes of the whiskers. The boxwex attribute is a scale factor that is applied to all the boxes; it improves the appearance of the plot by making the boxes narrower. The mtext() function places a text outside the plot area, but within the plot window.
In the case of continuous variables, outliers are those observations that lie outside 1.5 * IQR, where Inter Quartile Range or IQR, is the difference between the 75th and 25th quartiles. The outliers in continuous variables show up as dots outside the whiskers of the boxplot.
In case of bivariate categorical variables, a clear pattern is noticeable and the change in the level of boxes suggests that Month seems to have an impact in ozone_reading. The outliers in respective categorical levels show up as dots outside the whiskers of the boxplot.
There's more...
Detecting and handling outliers depends mostly on your application. Once you have identified the outliers and you have decided to make amends as per the nature of the problem, you may consider one of the following approaches.
Treating the outliers with mean/median imputation
We can handle outliers with mean or median imputation by replacing the observations lower than the 5th percentile with mean and those higher than 95th percentile with median. We can use the same statistics, mean or median, to impute outliers in both directions:
> impute_outliers <- function(x,removeNA = TRUE){
quantiles <- quantile( x, c(.05, .95 ),na.rm = removeNA )
x[ x < quantiles[1] ] <- mean(x,na.rm = removeNA )
x[ x > quantiles[2] ] <- median(x,na.rm = removeNA )
x
}
> imputed_data <- impute_outliers(ozoneData$pressure_height)
Validate the imputed data through visualization:
> par(mfrow = c(1, 2))
> boxplot(ozoneData$pressure_height, main="Pressure Height having Outliers", boxwex=0.3)
> boxplot(imputed_data, main="Pressure Height with imputed data", boxwex=0.3)
The output would be the following screenshot:
Handling extreme values with capping
To handle extreme values that lie outside the 1.5 * IQR(Inter Quartile Range) limits, we could cap them by replacing those observations that lie below the lower limit, with the value of 5th percentile and those that lie above the upper limit, with the value of 95th percentile, as shown in the following code:
> replace_outliers <- function(x, removeNA = TRUE) {
pressure_height <- x
qnt <- quantile(pressure_height, probs=c(.25, .75), na.rm = removeNA)
caps <- quantile(pressure_height, probs=c(.05, .95), na.rm = removeNA)
H <- 1.5 * IQR(pressure_height, na.rm = removeNA)
pressure_height[pressure_height < (qnt[1] - H)] <- caps[1]
pressure_height[pressure_height > (qnt[2] + H)] <- caps[2]
pressure_height
}
> capped_pressure_height <- replace_outliers(ozoneData$pressure_height)
Validate the capped variable capped_pressure_height through visualization:
> par(mfrow = c(1, 2))
> boxplot(ozoneData$pressure_height, main="Pressure Height with Outliers", boxwex=0.1)
> boxplot(capped_pressure_height, main="Pressure Height without Outliers", boxwex=0.1)
The output would be the following screenshot:
Transforming and binning values
Sometimes, transforming variables can also eliminate outliers. The natural log or square root of a value reduces the variation caused by extreme values. Some predictive analytics algorithms, such as decision trees, inherently deal with outliers by using binning techniques (a form of variable transformation).
Outlier detection with LOF
Local Outlier Factor or LOF is an algorithm implemented in DMwR package for identifying density-based local outliers, by comparing the local density of a point with that of its neighbors.
Now we will calculates the local outlier factors using the LOF algorithm using k number of neighbors:
> install.packages("DMwR")
> library(DMwR)
> outlier.scores <- lofactor(ozoneData, k=3)
Finally we will output the top 5 outlier by sorting the outlier score calculated above:
> outliers <- order(outlier.scores, decreasing=T)[1:5]
> print(outliers) | https://www.packtpub.com/product/r-data-analysis-cookbook-second-edition/9781787124479 | CC-MAIN-2022-27 | refinedweb | 8,510 | 56.45 |
# Binary Search
Searching is the method to search for a specific element in a group of an element. It needs a unique identity that is associated with the desired element. As a unique identity of that desired element has been found, the index to that desired element is returned. The index indicates the location or address where that specific element has been found in the list elements of the array. If the desired data is found, particular data has been returned. Otherwise, it returned a null value.
There are several categories of search algorithms such as:
* Linear search
* Binary search
* Interpolation search
* Hash table search
A binary search algorithm is an approach for finding a position of a specified value within a sorted array. Binary search is the fastest and efficient searching technique used to find an element's position in a linear array.
Binary search can be applicable only on sorted arrays. For binary search, data should be sorted first, and it must be organized in either ascending order if the data is in the form of numbers or in alphabetical (A to Z) order if it is in strings format. To apply binary search at an array of data in an unsorted form, it must be sorted first using a sorting process in ascending order and then applying binary search.
In this technique, the array should be sorted first, and then the searching process is based on finding the midpoint by dividing the array into two halves. The essential purpose of binary search is to search the midpoint. If the desired element is not found on the first check, then the array is more divided into sub-arrays by repeating the same procedure. The binary search difficulty rises with more number elements in an array. Binary search is usually recognized as a logarithmic search or half interval search.
**Working Principle of Binary Search**
Its working principle is based on the *"****Divide and Conquer****”* rule. A divide and conquer method works by repetitively breaking down a problem into subproblems of a similar sort till these become meek sufficient to be solved straight.
Let's understand the working principle of binary search with the help of an example. The precondition for binary search is that the array should be sorted. If the data is not sorted, we can't apply binary search on that array. So let's understand the concept of binary search.
Firstly read the search element from the user as an input.
In this array, there are a total of 10 elements from 0 to 9 and arranged in ascending order.
The next step is to search the mid element in the sorted list of arrays. Now, we are going to find a mid-element of the array.
Because we want to find the mid-position of the array to divide it into two halves. For this purpose, let’s say the left value is 'a' and the right value is ‘*l*’. In the array. So, the formula will become like this:
![Mid = [(a+l)/2]](https://habrastorage.org/getpro/habr/upload_files/013/3b8/6fc/0133b86fc38ae8c8af3704e5b4de8ee6.svg)Then comparison will be made between the search elements with the mid element in the sorted list. Suppose if 'x' is a searching element in the array, then there will be three cases.
***Case 1:***
If both elements are matched/found, then display *"****Given element is found****”* and end the function
![ X== array[Mid]](https://habrastorage.org/getpro/habr/upload_files/c6c/cbb/2f8/c6ccbb2f8c1015f06ed216b6cda14993.svg)***Case 2:***
If the desired search element is smaller than the mid element, then again perform the above procedure for the left sublist of the mid element.
![X = < array[Mid]](https://habrastorage.org/getpro/habr/upload_files/d90/e21/7f1/d90e217f1cf8fd4984eba223683a4827.svg)***Case 3:***
If the desired search element is larger than the mid element, then again perform an above process for the right sublist of a mid element.
![X = > array[ Mid]](https://habrastorage.org/getpro/habr/upload_files/9e4/8d4/2da/9e48d42dae6f92fceeae9a86633974ef.svg)Further, a similar process will be repeated till we reach the desired search element. If the element also doesn't match the search element, then display *"****Element is not found in the list****”.*
**Example**
Let’s consider another example to understand the concept of binary search. We have taken the following array having elements from 0 to 9 as shown below:
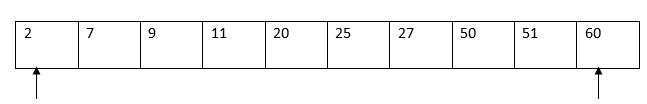Suppose if we have to search for 25. So the algorithm will check whether 25 exists in this array or not. If it exists in an array, then it has to return the index at which it was found. If it does not exist in that array, then it has to return -1. So, the first thing in a binary search algorithm is to define the range of elements to search. The leftmost position in the array is the starting index, and the rightmost position is the ending index. The next step is to look for the middle index. The index should be in integer form. So, we will take a floor value of 4.5, which is 4.In this way, the middle index will be 4.
The next step is to find the position of the searching element in the array concerning the middle. Now the middle element is 20. As searching element 25 is greater than 20. So, it will be present somewhere after 20. So we are only interested in elements to the right of the middle index. If A[Mid]< searching element, then search to the right of the middle element. Now search will start in this way, the starting index will be equal to Mid+1, and the end will remain the same.
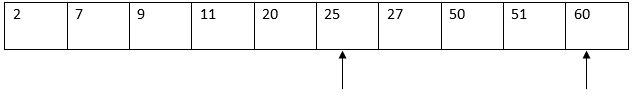Now, we again have to find the mid-index by following the same procedure as above.
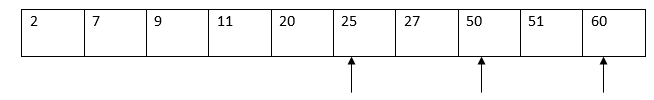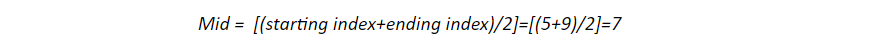The searching element that will be again checked is for the middle. In this case, the middle element is 50 at the 7th index position. So searching element 25 will come either left or right of the 50. As 25 is less than 50, so we will restrict our search to the left of 50. If the A[Mid]> searching element, then search to the left of the middle element. So, now the start will remain the same, and the end will be updated with Mid-1. Now the array will look like this.
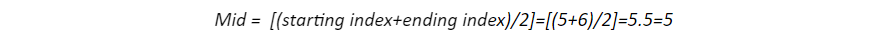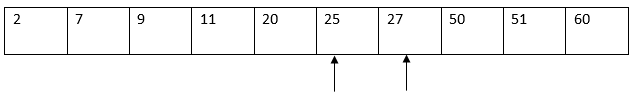We're searching for 25 in an array. And the middle element is also 25 at the 5th index position. And so we have found our searching element 25. And condition A[Mid]= searching element is fully filled.
**Pseudo Code/Logic of Binary Search:**
For that purpose, the binary Search function is used, which always stores numbers in integer format. In binary search function, there is a total of four parameters:
* Int ar[ ]: It is an input array that contains input data in ascending order.
* int x: It means left side element.
* int y: It means right-side element.
* Int z: It is a searching element.
If the left or zeroth element is less than or equal to the right (x<=y), it moves to the subsequent conditions. So, first, we need to find the mid element (x+y)/2, which will be stored in a mid variable whose data type is integer 'int'.If you need to search the particular element named 'z'. This specific element is compared with an array of mid "ar[Mid]".So, if ar[Mid] is precisely equal to z, it will return the middle element.
If the mid element is not matched with the searching element, it will go to the next condition. The next condition will be ar[Mid] > z, then find out the binary search algorithm on the left side. If the aforementioned conditions are false, it will move to the next condition that is ar[Mid]< z, and a binary search is performed. Finally, if the element is not present, then the return will be -1, which indicates the searching element is not in that particular list.
```
int bin_S( int ar[] , int x , int y, int z){
if (x <= y) {
int Mid = (x + y)/2;
if (ar[Mid] == z)
return Mid ;
if (ar[Mid] > z)
return bin_S(arr, x, Mid-1, z);
if (ar[Mid] < z)
return bin_S(arr, Mid+1, y, z);
}
return -1 ;
}
```
**Time Complexity Analysis**
For time complexity analysis, we need to take the worst-case time. This worst-case depends on the size of the array. The worst-case scenario is that we keep dividing the array into halves and searching for the element. And finally, we will come to an element in the range of search for which we want to search. And we realize one element in our range is not equal to the element we are searching for in list elements, and we say that element is not found. So this is how the worst case of binary search works. So let’s find the time it would take. In binary search, we have to perform the comparison of the search element with the middle element. If the algorithm performs a minimum number of comparisons, then it would be the best case. And if the algorithm performs a maximum number of comparisons, then it would be the worst case. The time taken to complete a maximum number of comparisons will be less than the time taken to perform a minimum number of comparisons. The best case would occur when the search element is equal to the very first middle element of an array. The worst-case will arise when the search element is present at the beginning of the array list or end of the array. In binary search:
* The worst case is "O(1)."
* The best case is "O(log n)."
* The average case is "O(log n)."
**Binary Search Tree**
Binary search in which for each node, the left child of that node is less than node, and the right child is greater than a node.
***Left Child < Node***
***Right Child > Node***
Binary search specialty lies in the fact that inorder traversal of this binary tree will result in sorted order of these elements. So, first, we must see the left subtree, then the right subtree of the binary search. Another essential property of a binary search tree is that it is easy to search for elements in the binary search tree. Therefore, we keep minimizing the range of searches using a binary search tree.
**Binary Search Tree Pseudo Code**
To understand pseudocode, let’s take an example in which we have to search for an element 5. First, we check whether the tree is empty or not. If the tree is empty, then the value will not be found. The binary Tree will be empty when there is no value at the root. So, in that case, the program will be returned null. Now in a case when a tree is not empty, we compare the searching element with the root. If the searching element is smaller than the root, then we must search in the left subtree. If the searching element is larger than the root, then we must search in the right subtree. If the searching element is equal to root, then it will return that element that has been found.
Figure 1: Binary Search Tree
```
var v = "Value";
var r = "Root";
var n = null;
var l = "Left";
function search(v, r){
if(r==n){
return n;
}
if(r.data == v){
return r;
}
if(r.data > v){
return search(v, r.l);
}
if (r.data < v){
return search (v, r.r);
}
}
```
**Advantages and Disadvantages of Binary Search**
**Advantages:**
* We search elements in complete input in linear search, but in binary search, we eradicate half of the list.
* It is one of the fastest searching algorithms.
* Binary search is consistently implemented on the extensive list of data. It works much better as compared to linear search.
**Disdvantages:**
* Binary search requires more memory or space in the computer.
* It requires more cache memory for a random access operation. | https://habr.com/ru/post/563652/ | null | null | 2,144 | 56.15 |
Yesterday. ‘hello.js’ and and rule.
function main() { return {payload: 'Hello world'}; }
wsk action create hello hello.js wsk rule create --enable sampleRule myCloudantTrigger hello wsk activation poll
When you change documents or add documents in your Cloudant database you can see logs in your terminal window and the OpenWhisk dashboard.
9 thoughts on “How to trigger OpenWhisk Actions on Cloudant Databases Changes”
Hi Niklas!
Thanks for this, exciting stuff!
I want to use the REST API, for doing this, but I don’t have the wsk CLI right now (I am on Windows…).
Would it be possible for you, or someone, to run the wsk commands with the -v option to output the REST API calls and show them on this page?!
Cheers
-jo2
I think I have the package binding working in REST API.
But the feed part seems harder, the REST API documentation is not that detailed on that…;-)
HTTP PUT
{ “binding” : { “name” :”cloudant”, “namespace” :”whisk.system” }, “publish” :true, “parameters” : [ { “value” :”mycloudantuser”, “key” : “username” }, { “value” :”mycloudantpw”, “key” : “password” }, { “value” : “”, “key” : “host” } ], “version” :”1″ }
Hi again!
I have installed wsk on my Mac now, and the example seems to work fine 🙂
I think the trigger creation command should be:
wsk trigger create myCloudantTrigger –feed //myCloudant/changes –param dbname –param includeDoc true
I.e. dbname is the parameter name (key property in REST API), and includeDoc seems to work. The documentation is somewhat unclear on this, so I tried both includeDocs and includeDoc, and includeDoc works.
I will try to gather the REST API calls corresponding to the wsk commands and post them here. My goal is to use the REST API to dynamically create triggers and actions.
Cheers
-jo2
Hi Jo, glad you made progress. Have you seen the Swagger API doc?
BTW: You can also use StackOverflow to ask questions and to get help from other/more IBMers.
Thanks a lot for the link to the Swagger API doc!
After running wsk -v, I realized why I struggled to get things working with only the REST API.
For example, the wsk command to create a trigger, actually ends up in TWO REST API calls…:-)
Cheers
-jo
————————————————————————————————————————
wsk -v trigger create wskTriggerCloudantChanged –feed ///changes –param dbname –param includeDoc true
========
REQUEST:
PUT
Headers sent:
{
“Authorization”: “Basic NN”,
“Content-Type”: “application/json”
}
Body sent:
{“annotations”: [{“value”: “///changes”, “key”: “feed”}]}
========
REQUEST:
Headers sent:
{
“Authorization”: “Basic NN”,
“Content-Type”: “application/json”
}
Body sent:
{“authKey”: “NN”, “lifecycleEvent”: “CREATE”, “includeDoc”: true, “dbname”: ” “, “triggerName”: “//wskTriggerCloudantChanged”}
——–
Nice article…
I have a basic question…
From the dashboard I see the trigger’s response is
mySampleCloudantTrigger
{
“changes”: [
{
“rev”: “21-10cc2e5a696af12d9432f907af8e9abf”
}
],
“seq”: “6035-g1AAAARbeJy90sFtwjAUBmCLIJUt4I6a2rGdwqlsUvJiuwkKBpFw4ARM0k7QFegmZYVOkBo7FPWGicTlWbLkX59-vwIh1MsCgZ4EpIuVnAiIwhzmj8uVLKVOZa7L_C2rSoxJmBaLtUh0FWpZFeZhJ0HQr-t6lgWAUNCfm7sHDpTx0dg_8b-CXa-AgZnwcoFsLASUwJIo_9Cb64DJCfJ6gRALSRmNqYjv2cj0BNn-QTo_DsIpxyN5x0Z010y0M4exvDeYvcVIICTGrVvhvpgPhzk0XzS0mEhESpGxf3DLZr4c5rtp5tNiKBOU8-e2zVBfzNFhzjuzdTsDNGYq8Q-e_QI4S2_1”,
“id”: “60774aec-dae1-4155-af60-8bc22517fbee”
}
Is there a way I can capture this response (or make use) in my action associated with this trigger (mySampleCloudantTrigger).
My intention to capture the ID which is affected in Cloudant database.
Hi!
Yes you can get to the ID in an action, after creating a rule which associates the trigger with that action (like the wsk rule command Niklas shows us).
I do not look for the ID specifically in my action (I look at some other property of the document from Cloudant), but you should be able to do something like in the actions main function:
function main(params) {
var id = params.id;
…
Cheers
-jo
Thanks Jo…I will try that. In addition to “id” i am using multiple other properties as well from the Cloudant.
Cool. Here is my entire action, with only the name of my other action masked.
stationfilter is a default parameter injected at creation-time of the action. Then I compare that (static) value with the corresponding property from Cloudant documents.
If matched, I call another OpenWhisk action to do further processing.
function main(params) {
var payload = params.payload || params;
var stationfilter = params.stationfilter;
if (stationfilter == payload.station) {
var name = ‘/myNamespace/anotherAction’;
var parameters = { station : stationfilter, doc : payload };
whisk.invoke({ name : name, parameters : parameters });
return whisk.done({ notify : ‘Station ‘ + stationfilter + ‘ == ‘ + payload.station, payload : payload });
} else
return whisk.done({notify : ‘Station ‘ + stationfilter + ‘ != ‘ + payload.station});
} | http://heidloff.net/article/how-to-trigger-openwhisk-cloudant | CC-MAIN-2019-30 | refinedweb | 678 | 54.42 |
Application wide settings can be a long conversation when starting a new application. Here are just a few questions when some of my teams started this conversation:
- Do we use ENV variables?
- What about manual bootstrap?
- Configuration files?
- Should we get them from the server?
Using angular-cli & environment.ts
The new angular-cli have the concept of different environments like development (dev) and production (prod). When creating a new application with the cli
ng my-app and /environments folder is a part of the scaffold which contains the environment files.
. ├── environment.ts ├── environment.prod.ts . .
and then within the /src/app folder is and
environment.ts file.
Here are the contents:
export const environment = { production: false };
As you might imagine, the *.production.ts file would have
production: true.
When the application is built (ng build) or served (ng serve), the environment.{env}.ts file from /environments is pulled and replaces the file within /src/app. By default this is dev.
In order to grab the production version, set the environment to production using the following:
#build $ ng build --environment=production #shorthand $ ng b -prod #serve $ ng serve --environment=production #shorthand $ ng s -prod
Adding additional environments -
not yet supported
If there are additional environments your build process needs to support, you can add more files to the /environments folder with the name of said environment such as
environment.qa.ts and then use.
#build $ ng build --environment=environment
One drawback here is there is no
-qa shorthand supported.
* Although the file is picked up by the CLI, there is a bug that the environments supported are only **prod or dev
Adding a "qa" environment.
Create a new file called environment.qa.ts in the /environment folder with the following contents:
export const environment = { production: false, envName: 'qa' };
Add the qa entry to the .angular.cli.json config:
"environments": { "dev": "environments/environment.ts", "prod": "environments/environment.prod.ts", "qa": "environments/environment.qa.ts" }
Now the new environment is ready to use.
Putting it together
First, add a new property to each of the environment.{env}.ts files.
export const environment = { production: false, envName: 'dev' };
Then in the
myapp.component.ts file import settings, and set the binding.
import { Component } from '@angular/core'; import { environment } from './environment'; @Component({ moduleId: module.id, selector: 'myapp-app', templateUrl: 'myapp.component.html', styleUrls: ['myapp.component.css'] }) export class MyappAppComponent { title = 'myapp works!'; environmentName = environment.envName; }
Finally, in the html template add the h2 tag.
<h1> {{title}} </h1> <h2> {{environmentName}} </h2>
Now if you serve the app with each of the
--environment={envName}, the binding will display accordingly. Note that the short hand
ng s -prod will not work for custom environments i.e.
ng s -qa, however you can use
ng s -e qa
Notes
Although this is a nice feature there are some things to point out as shortcomings, challenges etc.
only production or development are supported
- For every property that is added to the
/src/app/environment.ts, it must be added to the files in
/config/environment.{env}.ts, this is a disruptive workflow.
- Using this as a solution only works if you are building your application from source and not once then moving to each environment.
this may change! There is a current issue on the angular-cli repo addressing this very issue : Closed
- the
/src/app/environment.tsis only a stub per se and there to support the typescript compiler and serves no other purpose.
Enjoy, share, comment... | http://tattoocoder.azurewebsites.net/angular-cli-using-the-environment-option/ | CC-MAIN-2018-39 | refinedweb | 578 | 50.63 |
iPcCommandInput Struct ReferenceInput propery class. More...
#include <propclass/input.h>.
- RemoveBind: paramaters 'trigger' (string) and 'command' (string).
- RemoveAllBinds.
- LoadConfig: parameters 'prefix' (string).
- SaveConfig: parameters 'prefix' (string).
This property class can send out the following messages to the behaviour:
- (-1/1 is default).
- cooked (bool, read/write): use cooked mode instead of raw (default is raw.
- sendtrigger (bool, read/write): send out trigger name in the message to the behaviour. Default is false.
Definition at line 59 of file input.h.
Member Function Documentation
Activates the input to get Commands.
Binds a trigger to a command.
The triggername can be equal to 'key' in which case all keys will be bound.
Convert a coordinate from a value between -1 and 1 to screen-space.
- Parameters:
-
returns the command bind to a key
Get cooked or raw.
Is send trigger enabled or disabled?
Loads from a config file binding triggers(for example keys) to commands.
- Parameters:
-
deletes all binds
deletes a bind, if triggername is 0 deletes all binds to the command by doxygen 1.4.7 | http://crystalspace3d.org/cel/docs/online/api-1.0/structiPcCommandInput.html | CC-MAIN-2015-06 | refinedweb | 175 | 61.63 |
This is the third of a series of articles about Bayesian analysis. The previous article is here.
Earlier this semester I posed this problem to my Bayesian statistics class at Olin College:
This is an example of a mark and recapture experiment, which you can read about on Wikipedia. The Wikipedia page also includes the photo of a tagged hyrax shown above.This is an example of a mark and recapture experiment, which you can read about on Wikipedia. The Wikipedia page also includes the photo of a tagged hyrax shown above.Suppose I capture and tag 10 rock hyraxes. Some time later, I capture another 10 hyraxes and find that two of them are already tagged. How many hyraxes are there in this environment?
As always with problems like this, we have to make some modeling assumptions.
1) For simplicity, you can assume that the environment is reasonably isolated, so the number of hyraxes does not change between observations.
2) And you can assume that each hyrax is equally likely to be captured during each phase of the experiment, regardless of whether it has been tagged. In reality, it is possible that tagged animals would avoid traps in the future, or possible that the same behavior that got them caught the first time makes them more likely to be caught again. But let's start simple..
UPDATE December 5, 2014: João Neto posted a solution to this problem in BUGS using a Jeffrey's prior.
You should try Jeffrey's prior $p(N) \propto 1/N$ that can be normalized for any given M. This will make it more robust to changes of M.
Also, you could narrow the interval to [N-n+k,M] instead of [1,M].
ok, I programmed it in BUGS using the Jeffrey's prior :-) My solution suggests there are around 40 hyraxes for this data (I tried with a maximum of 500 and 1000 hyraxes, and the results were relatively stable).
The code and results are here
Cheers,
Hi João. Thanks (again) for your solution. It looks great!
I'm useless at stats, so please let me know if my answer is correct.
The first solution I came up with is:
If in a sample of 10 I capture 2, then that means that the population is 5 times larger than the number I've tagged. Since I tagged 10, there would be 50 hyraxes.
My second solution is using Python.
I assume they'll be at most 100 hyraxes as working assumption, and see how far that takes me. The approriate pmf is the hypergeom distribution. Given a population M, with a sample size N = 10, and number of tagged hyraxes n = 10, what is the probability of observing k = 2 tagged hyraxes?
So let me create a simple program and observe the output:
from scipy.stats import hypergeom
for population in range(11,100):
prob = hypergeom.pmf(k = 2, M = population, n = 10, N = 10)
print(population, prob)
The output shows a maximum probability at populations of sizes 49 and 50. They're the maximum likelihoods. So, 50 it is, then.
Regards,
Mark Carter.
Your solution looks good. But I encourage you to resist the temptation to collapse the posterior distribution to a point estimate (like an MLE, MAP, or posterior mean). One of the big advantages of the Bayesian approach is that you get a posterior distribution, which captures everything you know/believe about the value, and not just a point estimate or interval. | https://allendowney.blogspot.com/2014/12/the-rock-hyrax-problem.html | CC-MAIN-2021-39 | refinedweb | 584 | 64.91 |
In this tutorial, you will learn Python statements. Also, you will learn simple statements and compound statements.
Table of contents
What is a statement in Python?
A statement is an instruction that a Python interpreter can execute. So, in simple words, we can say anything written in Python is a statement.
Python statement ends with the token NEWLINE character. It means each line in a Python script is a statement.
For example,
a = 10 is an assignment statement. where
a is a variable name and 10 is its value. There are other kinds of statements such as
if statement,
for statement,
while statement, etc., we will learn them in the following lessons.
There are mainly four types of statements in Python, print statements, Assignment statements, Conditional statements, Looping statements.
The print and assignment statements are commonly used. The result of a print statement is a value. Assignment statements don’t produce a result it just assigns a value to the operand on its left side.
A Python script usually contains a sequence of statements. If there is more than one statement, the result appears only one time when all statements execute.
Example
# statement 1 print('Hello') # statement 2 x = 20 # statement 3 print(x)
Output
Hello 20
As you can see, we have used three statements in our program. Also, we have added the comments in our code. In Python, we use the hash (
#) symbol to start writing a comment. In Python, comments describe what code is doing so other people can understand it.
We can add multiple statements on a single line separated by semicolons, as follows:
# two statements in a single l = 10; b = 5 # statement 3 print('Area of rectangle:', l * b) # Output Area of rectangle: 50
Multi-Line Statements
Python statement ends with the token NEWLINE character. But we can extend the statement over multiple lines using line continuation character (
\). This is known as an explicit continuation.
Example
addition = 10 + 20 + \ 30 + 40 + \ 50 + 60 + 70 print(addition) # Output: 280
Implicit continuation:
We can use parentheses
() to write a multi-line statement. We can add a line continuation statement inside it. Whatever we add inside a parentheses
() will treat as a single statement even it is placed on multiple lines.
Example:
addition = (10 + 20 + 30 + 40 + 50 + 60 + 70) print(addition) # Output: 280
As you see, we have removed the the line continuation character (
\) if we are using the parentheses
().
We can use square brackets
[] to create a list. Then, if required, we can place each list item on a single line for better readability.
Same as square brackets, we can use the curly
{ } to create a dictionary with every key-value pair on a new line for better readability.
Example:
# list of strings names = ['Emma', 'Kelly', 'Jessa'] print(names) # dictionary name as a key and mark as a value # string:int students = {'Emma': 70, 'Kelly': 65, 'Jessa': 75} print(students)
Output:
['Emma', 'Kelly', 'Jessa'] {'Emma': 70, 'Kelly': 65, 'Jessa': 75}
Python Compound Statements
Compound statements contain (groups of) other statements; they affect or control the execution of those other statements in some way.
The compound statement includes the conditional and loop statement.
ifstatement: It is a control flow statement that will execute statements under it if the condition is true. Also kown as a conditional statement.
whilestatements: The while loop statement repeatedly executes a code block while a particular condition is true. Also known as a looping statement.
forstatement: Using for loop statement, we can iterate any sequence or iterable variable. The sequence can be string, list, dictionary, set, or tuple. Also known as a looping statement.
trystatement: specifies exception handlers.
withstatement: Used to cleanup code for a group of statements, while the with statement allows the execution of initialization and finalization code around a block of code.
Simple Statements
Apart from the declaration and calculation statements, Python has various simple statements for a specific purpose. Let’s see them one by one.
If you are an absolute beginner, you can move to the other beginner tutorials and then come back to this section.
Expression statements
Expression statements are used to compute and write a value. An expression statement evaluates the expression list and calculates the value.
To understand this, you need to understand an expression is in Python.
An expression is a combination of values, variables, and operators. A single value all by itself is considered an expression. Following are all legal expressions (assuming that the variable
x has been assigned a value):
5
x
x + 20
If your type the expression in an interactive python shell, you will get the result.
So here
x + 20 is the expression statement which computes the final value if we assume variable x has been assigned a value (10). So final value of the expression will become 30.
But in a script, an expression all by itself doesn’t do anything! So we mostly assign an expression to a variable, which becomes a statement for an interpreter to execute.
Example:
x = 5 # right hand side of = is a expression statement # x = x + 10 is a complete statement x = x + 10
The
pass statement
pass is a null operation. Nothing happens when it executes. It is useful as a placeholder when a statement is required syntactically, but no code needs to be executed.
For example, you created a function for future releases, so you don’t want to write a code now. In such cases, we can use a
pass statement.
Example:
# create a function def fun1(arg): pass # a function that does nothing (yet)
The
del statement
The Python
del statement is used to delete objects/variables.
Syntax:
del target_list
The
target_list contains the variable to delete separated by a comma. Once the variable is deleted, we can’t access it.
Example:
x = 10 y = 30 print(x, y) # delete x and y del x, y # try to access it print(x, y)
Output:
10 30 NameError: name 'x' is not defined
The
return statement
We create a function in Python to perform a specific task. The function can return a value that is nothing but an output of function execution.
Using a
return statement, we can return a value from a function when called.
Example:
# Define a function # function acceptts two numbers and return their sum def addition(num1, num2): return num1 + num2 # return the sum of two numbers # result is the return value result = addition(10, 20) print(result)
Output:
30
The
import statement
The import statement is used to import modules. We can also import individual classes from a module.
Python has a huge list of built-in modules which we can use in our code. For example, we can use the built-in module DateTime to work with date and time.
Example: Import datetime module
import datetime # get current datetime now = datetime.datetime.now() print(now)
Output:
2021-08-30 18:30:33.103945
The continue and break statement
breakStatement: The break statement is used inside the loop to exit out of the loop.
continueStatement: The continue statement skip the current iteration and move to the next iteration.
We use break, continue statements to alter the loop’s execution in a certain manner.
Read More: Break and Continue in Python | https://pynative.com/python-statements/ | CC-MAIN-2021-39 | refinedweb | 1,207 | 64.3 |
Final Destination
Bob and Khatu are stuck in matrix. The command center sent them a string which decodes to the their final destination. Since Bob and Khatu are not good at problem solving help them to figure out their final destination. They are initially at (0, 0). String contains L, R, U, D denoting left, right, up and down. In each command they will traverse 1 unit distance in the respective direction. For example if they are at (2, 0) and the command is L they will go to (1, 0).
Input:
Input contains a single string.
Output:
Print the final destination location of Bob and Khatu.
Constraints:
1 ≤ |S| ≤ 105
Explanation
if the input string is “LLRDDR”
Initail Postion : 0, 0
1.) ‘L’ -> cover one unit of distance in left direction. New position (-1,0)
2.) ‘L’ -> new position (-2,0)
3.) ‘R’ -> new position (-1,0)
4.) ‘D’ -> new position (-1,-1)
5.) ‘D’ -> new position (-1,-2)
6.) ‘R’ -> new position (0,-2)
#include <iostream> #include <string> using namespace std; int main() { string s; int x=0,y=0; cin>>s; for(int i=0;i<s.length();i++) { if(s[i]=='L') { x--; } else if(s[i]=='R') { x++; } else if(s[i]=='U') { y++; } else if(s[i]=='D') { y--; } } cout<<x<<" "<<y; return 0; }
Competitive coding
Hackerearth problem | https://coderinme.com/final-destination-hackerearth-problem-coderinme/ | CC-MAIN-2018-47 | refinedweb | 224 | 77.43 |
Hi,
I am trying to validate an XML file against a schema, which i can achieve without issue normally, however, in this particular schema, there is an imported namespace, that appears to be preventing the validation from happening, as the error being returned is pointing to node of the elements from the imported xsd.
I can manually enter the namespace refrences to the child elements of the XML file and it will validate correctly, however I cannot validate the document, by way of the code.
I have tried a number of things all to no avail:
I have added multiple XSD's to the XMLSchemaSet, which returned a duplicate declaration issue. I assume this is due to the top level schema having an import of the 2nd XMLSchema.
I also tried imports <, within the declarations, but this seemed to do nothing.
I have also been attempting to apply a namespace to the child elements that I can update manually. When the xDoc is validated against the applied schema it overwrites the previously correct element applied namespaces.
Can I add multiple schemas? am i doing something wrong?
Can i force something in during the validation of a schema.
Any advice would be appreciated here guy's. | https://www.daniweb.com/programming/software-development/threads/434392/xml-document-validation-against-schema-that-include-an-imported-xsd | CC-MAIN-2021-17 | refinedweb | 205 | 61.16 |
C API: Transliterator. More...
#include "unicode/utypes.h"
#include "unicode/localpointer.h"
#include "unicode/urep.h"
#include "unicode/parseerr.h"
#include "unicode/uenum.h"
Go to the source code of this file.
C API: Transliterator.
The data structures and functions described in this header provide transliteration services. Transliteration services are implemented as C++ classes. The comments and documentation in this header assume the reader is familiar with the C++ headers translit.h and associated documentation.
A significant but incomplete subset of the C++ transliteration services are available to C code through this header. In order to access more complex transliteration services, refer to the C++ headers and documentation.
There are two sets of functions for working with transliterator IDs:
An old, deprecated set uses char * IDs, which works for true and pure identifiers that these APIs were designed for, for example "Cyrillic-Latin". It does not work when the ID contains filters ("[:Script=Cyrl:]") or even a complete set of rules because then the ID string contains more than just "invariant" characters (see utypes.h).
A new set of functions replaces the old ones and uses UChar * IDs, paralleling the UnicodeString IDs in the C++ API. (New in ICU 2.8.)
Definition in file utrans.h. | http://icu.sourcearchive.com/documentation/4.8.1.1-1/utrans_8h.html | CC-MAIN-2017-39 | refinedweb | 206 | 60.72 |
So I have a table representing an business entity that has a one to many relationship with a table representing work items for that entity, the schema is basically this: BusinessEntity ID Title ...a bunch of other fields WorkItem ID BusinessEntityID
Say I have the below set of data where I wish to group the Description column based on whether the dates for matching Descriptions are within a few seconds of each other. The output I'm looking for is the Description and the minimum Date for that gro
i just don't understand the meaning of writing AsEnumerable() in linq query. i am having one UserDetail table in which i am fetching all details of user and i want to take name,email in to my model. var data = context.UserDetails .Select(temp =>
I am trying to build a dynamic menu that uses Identity 2.0 roles to define what menu items the user should see. I am very new to C# and need some help please! For the purpose of what I am doing, I am thinking of a Role as a Menu Item that a user can
The following code worked until I moved to Asp.net Framework 4.5. var dateAndPort = (from c in context.CruiseCalendar where c.ShipId == sourceId && c.CruiseDayDate >= dateRange.Start && c.CruiseDayDate <= dateRange.End select ne
I have the following entities. Category, Topic, Post, Member. They are related by the following Category has a list of Topic Topic has a list of posts Post has a Member Below are the classes public class Category { public Guid Id { get; set; } public
I have code below. I would like insert a new record into sql-server via entity frame work 5.0. Unfortunately, it is failed. After click save button the record does not in to database. Anybody can help me out would be great appreciate. @model IEnumera
The SQL below returns a count of records updated by week. I have recreated in linq the part that returns the count by week(below) but I can't get the startofweek and endofweek columns. Help SQL select DATEPART(wk, audit_date) week, count(audit_date)
I hope you can help me with that. I have a very simple query running on oracle with the ODT managed provider: return Ent.TABLE.ToList(); witch gives me 34k records, but it's taking as long as 45 seconds to give me the result, but if I run the query (
I want to reuse mapping in select statement. I'm not able convert sequence to list, array and so on, because query is used in web api with odata and I don't want to extract all data if odata query reuires only one page. Currently I'm using expression
I have User entity and related to many product entity , I need a way to get the user entity with subset of its products not all the products. var user = User.Include("Product").ToList(); // it returnes all the products. I need a way to return the Use
i tried to solve one query from last 2 days but didn't It looks easy to understand but can't made There are two column in Table for Ex. ResourceId || MappingId 1 2 1 3 2 2 2 4 3 2 3 4 4 2 4 5 5 2 5 4 This is one table which have two fields ResourceId
I have two lists as follows: var SeparatedEmployees = (from s in DataContext.HRM_EMP_TRMN.AsEnumerable() where s.TRMN_FINL_STUS == "SA" && ((Convert.ToDateTime(s.TRMN_EFCT_DATE)).Year).ToString() == Year && ((Convert.ToDateTime(s.TRMN
I'm using LINQ to Entities to fetch elements from a MSSQL data base and I need them sorted by the last index of a string: var data = db.GetEntities(). OrderBy(e=>e.StringProperty.LastIndexOf("Foo")).ToList() However, LINQ to Entities does not supp
I need to remove leading zeros from a string. I'm trying to use TrimStart('0') in a linq to entities query and its not supported. I found this related question, but that solution didn't work for me, it says that function is not supported either. Any
I have a Clinics table in SQL2008 which has nullable decimal Latitude and Longitude columns (nullable as I don't have coords for all clinics). I'm using Linq-to-EF and would like to calculate / sort the records by the distance from a given point. For
How would I generate the following using expression trees... var people = context.Set<Person>(); var transactions = context.Set<FinancialTransaction>(); var dataview = people.Where( p => p.LastName == "Smith" ); var selection = datavie
I have got two entity POCO entities with many to many relationships, e.g. public class Employee { public int Id; public string Name; public virtual ICollection<Organization> Organizations {get;set;} } public class Organization { public int Id; | http://www.pcaskme.com/tag/linq-to-entities/ | CC-MAIN-2019-04 | refinedweb | 801 | 64.1 |
2:07 pm
What’s the point with making UI simple if you can’t do what you want it to do, the way you want to do it? There are users out there who do not want UI designers making too many decisions for them by limiting what they can and cannot do. I rather have too many choices than no choices at all. Gnome, in its current state, is taking too much away from users that some people feel their intelligence is being insulted. I’m being one of these people.
This article is somewhat related to the issue:
In my opinion, this matter is so clear that Linus could understand it if someone would explain it slowly to him: different users simply have different needs.
Not all users want to fiddle with every knob – some users just want to get their work done. Some users care about aesthetics and some do not. Giving a user choices she doesn’t understand is often even a security hazard.
It’s interesting to see that usability has obviously never been a design goal for Linus Torvald when he wrote the Linux kernel. Linux is about hacking and tweaking by design – looks like a hobbyist thing to me. It’s not a coincidence that other Unix/BSD systems give users a far more clean and consistent experience, because some projects take these things seriously as a design goal.
…and just because Linus is a public figure with influence does not exempt him from having one. I saw no personal attacks, but clear and concise criticism in his comments. He is entitled to complain or make suggestions just like everyone else. Surely the size of his contribution to the community should earn him the right to make valid suggestions and criticisms of a project that he disagrees with. Quit acting like he betrayed the community.
I agree with Linux entirely, though it is dangerous to say such stuff around here (I would not phrase my opinions so roughly though). His reasons for preferring KDE are my reasons.
Those are my reasons *for myself* though. Unlike him, I am not as certain about reasons (or lack of them) to recommend one over the other for the general public.
“If you think your users are idiots, only idiots will use it.” This is very harsh sounding on the surface. However, Gnome is trying to be a project for the average computer user, and the average computer user is a computer idiot (face it, people want their computers to work like their toaster, and want to have knowledge of how they work). I think Gnome fails in some of their goals, but they actually are aiming at the (computer) idiot as Linus says.
That doesn’t mean KDE isn’t as well, but they do (IMHO) a better job at also reaching out to the advanced users, the type of user who would realistically actually be using Linux right now.
And of course plenty of advanced users like Gnome, so one can’t say Gnome leaves them out in the cold either. Things are obviously not black and white. KDE can work for the newbie (ask Xandros) and plenty of advanced types prefer Gnome.
Still, my reasons remain valid for me, and they are pretty much what Linus enumerated. Choice remains for those who feel differently, and Linus won’t be taking that away, so we can continue to have our two big DEs and the lovely discussions about them
Some more cool replies from him:……
PLEASE READ THEN MOD ME DOWN/EXPRESS YOUR FRUSTRATIONS — BUT I DO WANNA KNOW WHAT YOU GUYS THINK
Hi, I just want to add my 0,02$ because I think we are all concerned about this. The never ending KDE vs Gnome battle is almost like the Linux vs no Linux battle. It does matter. And I do believe that the WM in a Linux distribution is the number one factor of its success. Not only its success, but Linux success.
I do agree with Linus. Gnome sucks. Why? Linus said it all. It doesn’t do what you want most of the time (unexpected behaviors) and it forces you to use it in a way you probably don’t like. Take for exemple the font config dialog of Gnome. What the … is that? Best shapes, best this, best that. OMG. Can I be free to consider what is best and what is not? This is one single exemple but there are others. Why not just allow me to pick up fonts and set properties like Anti-Aliasing directly? WAY LESS CONFUSING. And I don’t believe in the Gnome number one excuse: “it would confuse too much people”. Lies. These folks are just unable to deliver alot of changes within an acceptable amount of time. Yes, I do believe that Gnome developers are way less experienced than KDE ones. Gnome is still way too much simplistic after all these years…
So, all you guys want to tell me: use KDE and shut the … up for god sakes! But it’s not as simple as that. Like I said, the WM is the number one factor of a distro’s success (for most people). We all know it’s pain in the ass to use a Gnome centric distro (like Fedoracore) when you want to use KDE. Everything is GTK based and the KDE integration isn’t really good. Finally, you really do have to pick up a KDE centric distro but they are rare these days (enterprise level). You have SUSE (now OpenSUSE for me) and Mandriva that I don’t really like. (Don’t tell me Kubuntu, I know it exists but I’m talking about enterprise level distros with enterprise level tools, think about RedHat…). It’s kinda hard to be happy you see? And it’s getting even worst with news like SUSE is about to drop KDE (probably not true anyway).
Anyway, that’s my opinion. And don’t think I’m a KDE fanboy because I’m not. KDE is problematic too but way less than Gnome. The number one problem is probably the fact it was made for blind people (sorry we are no more in the Windows 3.1/Windows 95 640×480 era folks) and when you want to use it high res with small icons it just behaves weirdly sometimes. Also, there should some Advanced settings tabs everywhere so it would please people that believe that KDE is too complicated. Finally, it really needs a better look (why is KDE4 taking forever? 🙂 and they need to change some of the basic behaviors to match popular GUI ones (Windows,OSX). But anyway, I do believe that one day they will do it all because they are talented after all.…
2005-12-13 2:03 pm
“And it’s getting even worst with news like SUSE is about to drop KDE (probably not true anyway). ”
SuSE will not drop KDE, but they will be gnome-centric. ie, they will certainly drop many k* applications off the CDs in favor of some gnome apps.
You *can’t* have the same level of gnome and kde app on the same cds. Only debian can pretend this. (btw, they install gnome by default)
Fedora got 4 cds and they have nothing interesting for kde. SuSE will go through the same path ! gnome-centric, f–king crap.
You can count the number of *good* distro that’s DM agnostic in just one hand.
Debian, Gentoo, Slackware. That’s all.
There is no GOOD pro-kde distro. Mandrake is not pro-kde, even if in the birth of the distro they were just a redhat with kde. A very large number of Merdrake users are gnome lovers too.
Kubuntu and Ark Linux are jokes.
We seriously need a good, all-public distribution that support KDE ! gentoo and slackware are not for newbies and debian stable is going through the obsolete path. I’ve got some fear when i think of the kde fate. There’s no good newbie distro that support it, that’s really sad. SuSE were really good but novell will screw it in its next version.
-
-
2005-12-14 11:13 am
“Wrong again, they install both, they just use gnome and gdm by default. But KDE is there.”
stfu, the last time i tried a debian netinstall with sarge it installed me gnome but no kde by default. I saw some libs but not the true desktop.
Myself i don’t really care of the default install. Just wipe that out, apt-get install x-window-system kde and it will rock.
-
-
2005-12-13 2:23 pm
” Please people, if you don’t have any constructive arguments then stop posting here. But please also stop spreading false statements and pure FUD.”
The corp. editions of the novell linux will be gnome-centric, and i can’t imagine they will really make a parallel opensuse edition that will be as KDE-centric as today. Waste of resources.
Novell is not about charity, but rentability. They will sell gnome based, not the actual opensuse. Opensuse ? they don’t care.
-
2005-12-13 2:30 pm
” Novell continues supporting KDE as well as GNOME as they did before. SUSE will default to KDE as it used to be but also offers GNOME as option.”
I don’t say they will *drop* kde, i’m saying they will be very less kde-centric.
There is five CDs in suse, and a VERY LARGE percentage of KDE applications.
There is four CDs in fedora, and a VERY large percentage of gtk/gnome applications.
You can’t have the two, or your name is debian and you got 12 cds to sell.
Fedora support a KDE, but crippled, with very few kde apps in the distro.
Suse used to support a crippled, old gnome, with few gnome apps.
Now, Novell will be gnome-centric for their corp work. And, they don’t do charity, so they won’t maintain the same level of KDE-friendlyness as before on OpenSuSE.
-
2005-12-13 2:39 pm
YOU are the shit.
.
“The entire KDE graphical interface and product family will continue to be supported and delivered on OpenSuSE,” said Mancusi-Ungaro.”
They will serve a less kde distro. Because if they want to add a certain number of gnome apps to make it ready to be the default desktop, they can’t have the same number of apps, or they will need to add more CDs to the distro and it will be the new debian.
2005-12-13 2:43 pm
> YOU are the shit.
You are disqualified.
The announcement you quoted was Novell’s first shot out. They instantly row back after some heavy noise from the public. They corrected their statements and clarified that everything is as it used to be with the only exception that there is a GNOME option in SUSE.
2005-12-14 10:14 amdefile
“And I do believe that the WM in a Linux distribution is the number one factor of its success. Not only its success, but Linux success.”
I’m curious as to what your metric for success is. According to this:
Rank Distribution H.P.D* (Hits per day)
1 Ubuntu 2623
2 Mandriva 1686
3 SUSE 1611
4 Fedora 1082
5 MEPIS 937
I think we could safely say that Ubuntu tends to be Gnome centric. Granted these numbers don’t tell the whole story for a couple of reasons. Distrowatch isn’t the only source on the planet for finding a distribution (but I’d say it’s a major one).
Results 1 – 10 of about 1,820,000 for distrowatch. (0.10 seconds)
People can also change the WM to whatever they want once it’s installed.
You then go on to say:
“Finally, you really do have to pick up a KDE centric distro but they are rare these days (enterprise level).”
Maybe there are some valid reasons for that. I could give you mine, but it would be speculation on my part and might be completely off, or may give an impression of my personal bias that I don’t wish to convey.
IMHO your entire comment came off as a tirade to me. What was your point? Gnome is the suXorz because it’s too simplistic and less “Enterprise” distributions are supporting KDE? Gnome/GTK centric distributions make using KDE/QT have crappy integration? All of the above?
And finally:
…”
SUSE has always been over it. Mandriva, back in the days when it was called Mandrake, was born due to Red Hat 5.0 only coming with Gnome for a DE (even when it was utter crap. Basically a panel and used FVWM for a Window Manager (its only redeeming feature IMHO)). Mandrake Linux’s initial claim to fame was as a Red Hat compatible distribution that came with KDE by default (very nicely configured). In short, Mandrake/Mandriva has always supported KDE/QT to begin with. There was nothing for them to “get over” either.
Red Hat’s commitment to Gnome has been because they have so much stake in it as far as money/developer time/promotion (which all equate to money, really). IIRC, until Red Hat 7.0 came out, if you wanted KDE on it, you had to either download third party RPM’s (some were better quality than others), or compile it from scratch. Either way, it fell on the user to do post install.
-
2005-12-13 1:43 pm
> i feel sooooooo sorry for poor linus. he’s going to
> have one hell of a hangover and bad feeling when he
> wakes up in the morning and realises the total crap
> that he came out with the day before. poor linus
Don’t worry about him. He’s doing fine and probably has tons of people protecting his back – and I am included here.
2005-12-13 4:42 pmeMagius
kde sucks bad ass when compared to a vanilla OSX desktop, but GNOME? – man twm has more functionallity than gnome.
twm has more functionality than KDE as well. I don’t see the point of these bloated candy-coated, buggy, extraordinarly limiting interfaces for anyone who’s not a beginner. IceWM, Fluxbox/Blackbox, fvwm, etc. (+ desktop icon manager of your choice if you’re noob enough to rely on desktop icons) run circles around both KDE and Gnome in functionality, customization, stability, and performance.
about the Gnome project that bothers me is that it is increasingly the choice for corporations. I feel that the feature delete that Gnome is experiencing is the result of pressure from large corporations who are more concerned with keeping sheeplike, cubical bound workers on task. Providing features gives workers more flexibility and more chance that they will get off task. It is well know that Gnome is very heavily influenced by Novell $$$, and one of their best designers is a Novell employee. I prefer KDE because it has not yet succumbed to the agenda of big business. This is, of course, only my opinion based on personal observation.
Edited 2005-12-13 13:44
Is this F.I. a new short term for f–king Idiots or I am missing something? The fact that I am using KDE and support it doesn’t make me any better than GNOME users. I support the GNOME users in any mean, what they do, how they work, their community at all, although sometimes I use to make light jokes for things that seem funny in the work of GNOME with my close GNOME-using friends. But this is no joke anymore and seems to make another flame war between the users of the free software. It is like, I am not using GNU but rather Linux or I will throw Linux from GNU/Linux and use GNU only. Which is not possible.
We have right to choose, Linus is nothing more than a kernel creator and ego-centric hacker who thinks has the right to call the users of Linux based OSs to use this or that, however there are some blind “followers” of his idealism and will agree on this, as much as there are the hardcore GNOME users which will try to deny what the first ones would say and that is war. However if you are sane and think twice, you all stop here, even lock this article for replying cause it leads to haterd and that would lead to making differences in the core of the open source community which is the less thing we want now, don’t we?
Aleksandar,
Macedonia :
Just my 0.2€ ( and I’m french
)
2005-12-13 1:48 pm
>
>
>
More unfixed GNOME Print bugs:
And hey, these are just for trivial printing stuff.
2005-12-13 1:52 pm
> It has just a simple solution to the GNOME problem that
> doesn’t make the system hard for starters: put an
> advanced tab on the systems configuration options!
>
> It’s hard to do that?
Yes it’s that hard. Due to GNOME’s ugly framework these things are not easy to implement and requires a disciplined change in many areas..
For the record I am a GNOME (and Mac) user. I would consider my self a tech user (ie I code, most used apps – vim, xterm).
I have no problem with GNOME dumbing down interfaces. I actually think this is a good thing. But why they hell cant they provide an “Advanced” button or Tab to let people (who want to) have more config options.
Too many times the GNOME group act like Nazis – example when they changed Nautilus behavior some time back (open folders in new windows) and did NOT provide a way for people to configure it back to the old design. yes I know it is possible to google and find out how to do this but why was the config option not in GNOME?
On the other hand calling designers FIs is not really going to make them listen to you. Linus’s approach is not constructive – only good for a flame war
Interesting set of comments. Most are more cogent and helpful than the original post being commented on, thanks. As an “elderly” user of the computer world, these type of extended commentaries are very useful to me. I pick up lots of small and ancillary things that I can then test to see what they do. Oh yeah, by “elderly” I should add that I’m 67, male, retired (small income, durnit), reasonably healthy, and haven’t lost my mind yet (although posting this might belie that).
I have three computers set up, even though using a slow dial up connection, and they are all using different systems. The main one is Debian Sarge, Gnu/linux running the Gnome environment (did I get that right?). Another is a Windows 98 system on it’s last legs and used to play the books-on-tape from Audible.com since I’m not enough of a geek to have figured out just yet how to get wine or something else to run the Audible material. Another, formerly a Windows XP system and now a happy test system, is used to run any kind of “distro” that catches my attention and I feel like paying the toll to have sent in. It has run quite a few systems, every thing from Symphony to SUSE and Puppy. Right now, it’s a Debian Sarge Testing system to keep me from crashing the other Debian Sarge Stable (at least for the moment) system.
While that doesn’t give me any credentials to discuss things on the level of Linus Torvald, I’m still the most important person in the Linux world. I’m the “end user” and no one is more important. If it’s not used, it just dies, no matter how wonderful it is. Think about all the Linux software that was started, showed great promise, and simply faded. Some of that was potentially able to change the computer world but didn’t get used. Us little people make it all work.
While I’m presently using Gnome I have used KDE extensively. Lots of good to both and some not so good on both. Yes, Gnome might suit the elderly, not so smart, casual computer user better than KDE. Good for them (not to say Gnome was written for AARP). KDE might be written for the more involved user or possibly those users with a few more cerebral cells remaining. Good for them. Isn’t that kind of important? Lots of choices? I’d like to try even more environmental systems to see what fits the elderly but still curious human (well, even the elderly are still human, you know).
Linus Torvald’s remarks indicate a focus on what he’s doing and it is important to him. Doesn’t especially help me, the end user, unless it improves the environment I find in my computer. I don’t care much about speed (retired and on dial up, remember) but I do like to be able to mess with the system some. I think of it like a large sponge ball with lots of decorations pinned to the outside. I want to play with the decorations, not crawl inside the sponge ball that’s holding up the decorations. Probably most end users feel the same.
All in all, the comments generated by Mr. Torvald’s statements (if he did, indeed, say them) are more interesting and useful to me than the original Torvald statement. So, once again, thanks.
I just wonder.
He tried to code linux with c++, and he told us it sucks.
I guess, May be GUI implementation wih c++ is different.
pygtk, gcj(java-gnome), ruby(ruby-gnome), mono all is all and good for me.
I am using garnome-2.13.2 with LFS-style debian.
When i was a kid, i used to use kde. and i grown up.
Here in the third world, which means most of the world, IceWM, Fluxbox, and Ion3 rules.
KDE and Gnome are products for the first world users with new computers that no matter how fast, can’t keep up with the bloat of the software.
These entities should stop wasting our time and dedicate their valuable time to things that are important like wifi, lean/fast software, accounting and cad software.
It’s a sad day to be a Linux user – to realize that a pillar of the open source movement would be so rash to call people he disagrees with “f–king idiots.” If only the Ubuntu code of conduct applied to the whole FLOSS community.
I’m reminded of a scene in “Just for Fun” (a book about Torvalds from a few years back) where Linus is visiting the author’s house and notices the author’s Mac. He sits down and complains about the display and tries to change it to his liking. He complains that he can’t do what he wants on the Mac.
While I’m sure the PPD options are needed in some situations – where corporations have $10,000 printers, etc., for cases like mine (running a small business) GNOME provides much better for my needs. In GNOME, I plug it in and it shows up. I like this. And in GNOME, NetworkManager makes using my wireless card painless. And GNOME Volume Manager does the same for CDs, DVDs, floppies, iPods, etc.
By and large, I really like what the GNOME crew have been up to. There are CERTAINLY problems here and there, but they are have little to with mouse button assignment and the like. So, in conclusion, almighty and ever-righteous Linus Torvalds, drop the attitude, refrain from calling the people who have made Open Source accessible to me and my business “f–king idiots” and learn to treat the work of others with respect. Otherwise, I’m moving to a BSD.
“In GNOME, I plug it in and it shows up. … And GNOME Volume Manager does the same for CDs, DVDs, floppies, iPods, etc”
KDE desktop -> right click, configure desktop -> behaviour -> device icons.
Or
Kicker right click -> add applet to panel -> storage media.
Insert CD/thumbdrive/whatever, see it appear on the desktop or in the kicker. Granted, setting it up for the desktop is a bit buried, but one only does it once
or the distro does it for him.
That is something that should be on by default I think, and Gnome is right to have it so. It is there in KDE though, and by default too with Kubuntu and others.
In an earlier comment I mentioned that Gnome was in fact aiming at (computer) idiots, that is to say potentially brilliant people who don’t care to know how a computer works. Linus is right to say they do.
Just thought I’d back up that assertion:
.” – Jeff Waugh, from the discussion the article linked to (emphasis added)
Why doesthis stupid argument go on and on and on. People can choose their own WM or DE on *nix and that’s the way it should be. Why must there always be people who want to tell others which one to use. Anyway everybody’s got their own opinion on this. It’s just one more of those stupid my Desktop’s better than yours discussions where somebody wants to feel good about calling others stupid for not using theirs.
Didn’t believe Linus to be that religious about his preferred software.
Sorry if my English isn’t all correct. Not a native speaker.
First the lawship against people who use his copyrighted name (Linux) then this shizoid article about interfaces..
The big advantage of Linux (can I still use the name Mr Linus??) is its openess and freedom of choice, even users of KDE benefit from the existance of Gnome and all other interfaces. Why’s this anger Mr. Linus?
use of the word “Nazi” don’t you think?
2005-12-13 7:40 pmdylansmrjones
No not really.
It’s pretty common in many countries.
Using nazi or fascist in combination with other words are pretty common, at least in Denmark.
Interface Nazis would in Denmark probably be Interface Fascists but that’s the only difference. Interface Communists could be another good term to show that somebody are abusing their position to force people to do something a specific way.
It’s good someone of real importance is showing that he isn’t bowing down to what we find politically correct, for lack of better terms, in the computing world. The man prefers KDE, and he’s not scared to tell you that, no matter how much you gasp or groan. I applaud Linus. Now, what on earth is the man talking about? KDE’s a dog
Yeah, guess that’s my opinion *grin*
This isn’t a debate about Gnome or KDE, or KDE versus Gnome. Who cares. This is really about the degree to which Linux (or elements of it, like the desktop environments) listens to its users and tries to make them welcome.
It’s fairly clear that elements of Linux do not listen to their users. Far from it. Gnome generally doesn’t. They’ve set a clear course and implement “Do it our way or hit the highway.” Not surprisingly, some folks don’t like that attitude and I can’t say I’m surprised.
Together with this, there are some crude and unattractive attitudes towards end-users. The talk about morons, bright users and hackers is a giveaway. Those who treat other users (i.e., other people) as idiots or “newbies” have no concept of service and no place serving up open source software. Mentally, they haven’t yet grown up and left school.
There’s more than a trace of this in Gnome (and a huge element of it in distros like Debian). No wonder people can be repulsed and become annoyed. Totally understandable. I’m glad Linus Torvalds has enough humanity and common sense to call out some puffed-up twits then he sees them.
This is pretty much a non-issue IMHO. Who cares what Linus Torvalds thinks about a DE and GUI and how they function? It’s largely a matter of personal taste and what each individual user finds comfortable for what he/she does with a computer. Linus should avoid ex cathedra prnouncements on anything other than his kernel.
2005-12-13 3:35 pm
i agree. nobody should care one bit about what linux thinks about the UI. he is the kernel writer, not a designer. its a bit like the maker of the engine telling ferrari how to design the appearence of a car.
so, linus, why don’t you just belt up and stick to what you know and shut the f up about what you don’t.
-
2005-12-13 11:38 pm
“i agree. nobody should care one bit about what linux thinks about the UI. he is the kernel writer, not a designer. its a bit like the maker of the engine telling ferrari how to design the appearence of a car.”
Yeah, nobody should listen to potential users’ opinions. At least not if they aren’t interface designers.
Way to go OSNews! Congratulations! You bought into the ranting of a troll hook, line and sinker, and trashed Torvald’s reputation at the same time. Nice job!
I mean come on… Did you read some of the follow up posts? Cursing? all caps, illogical arguments, etc? This is clearly not really Linux posting. It is a troll using his name.
OSNews is getting to be worse than Slashdot when it comes to not verifying whether their info is accurate, and posting sensationalist headlines in order to boost read count and reply count.
What happened the OSNews that uses to be a legitimate news site? It sold out to the wanker wannabes, just like slashdot did.
-
2005-12-13 3:24 pm
If it really is Linus, then I must say it is truly sad that he has decided to join the “immature asshole zealot” camp of Linux hackers–the camp that derides and ridicules other people for having an opinion different than their own. They are a dark stain on the entire Linux community–especially when the founder himself decided to join them.
2005-12-13 3:27 pm
> “immature asshole zealot” camp of Linux hackers
Sorry I can not confirm this. Linus Torvalds was always very friendly and calm to me whenever I contacted him. Though I am one of the SCSI driver Maintainers (amongst two other buds). Linus was always correct and honest. All I can see in his reply was, that he finally set the butts of the prideful GNOME crowd who believes to be correct in all they do on the pot. And hey, they deserved it. There are no bigger egos and assholes than those from the GNOME camp.
-
-
-
I like Gnome’s mentality quite a bit. For some reason, I never could find the need for a powerful windows environment for power users. Everything I need is in the command line. I just need my desktop environment to open Firefox, Thunderbird, OpenOffice, a few video-editing applications, and I need it to be able to print. I also want it to get out of my way as much as possible (not too flashy, not to clutterred, not too complex) so I can concentrate and think right. Otherwise, I don’t care what it does, how it does it, or how it looks (as long as it isn’t hideous like KDE
is.)
A lot of people seem to forget that Linus is human and has his likes and dislikes just like the rest of us. He likes KDE? Kudos and bouquets for him.
Just because the benevolent dictator likes KDE and not GNOME does not make GNOME users scum, nor does it make KDE users gods. Free software is about choice, and no desktop environment pundit, pro-KDE, pro-GNOME, or otherwise can change that fact.
Everyone who is getting so heated and passionate about this debate needs to have a cold one and relax. Hell, I love Linux while my wife hates it, yet we are able to be civil about it, even if she is a little Windows loving… (just kidding 😉 )
Why can’t we learn a lesson from the Swiss? :-p
2005-12-13 3:45 pm
Well, I don’t much care what Linus thinks about Gnome vs. KDE either. But Linus really needs to either learn how to have civil dialog, or get someone to sanitize his posts for him. It’s just very bad PR for someone in such a prominant position in the Linux community to be trashing others in his own community with that kind of venom spewing forth from the hole in his face, and and it reflects very poorly for him to resort to childish antics like all caps cursing and such.
GNOME has serious problem in their UI design and lack of function. I can see GNOME somtimes is trying to learn from Mac OS X’s simplicity. However, they don’t really understand Mac OS X. As a former KDE user and now a Mac OS X user, I can see Mac OS X is the easiest to use, and also looks simple and elegant. Compared with GNOME, GNOME simply “looks easy” but using it is a pain. Mac OS X looks simple, but it has so many advanced tricks which can give you a lot more effiency. KDE may have too many options for you to choose. It is a problem but KDE is also easy to use. Their problem is that KDE needs to hide more options in ADVANCED bottons.
Hey guys STOP trolling for nothing ! This is free world everybody can have his own opinion but yours !
You like Gnome use it, personnaly I use what can be used !! => KDE or Gnome ( I’m not going to be that sort oh hayatolah installing a DW just for console lines
) depending on linux distro I’m on … and on personnal computers fluxbox / fvwm / blackbox depending on time I have to customize and size of RAM …
That’s it !
I’m so sick of this egocentric world of linux where everybody tells you his own truth … You got a problem ?
Answer 1 : try another soft / command line …
Answer 2 ( after trying answer 1 ) : recompile !!
Wher is the “Keep It Simple Stupid” mind nowherdays ?!
Linus and I can agree on something!
Well, I don’t agree for the same reason he does, but I do agree that KDE is champ. In my opinion, KDE is more technically advanced and generally a better looking desktop.
That being said, the only thing that holds KDE back from corporate adoption is the GPL. Let’s say if I, as a corporation, want to use KDE in order to develop closed-source applications then I’d probably a) need to get a Qt license, or b) just GPL everything I develop. The problem is, I don’t know for sure if option “a” protects me fully. I mean, I think other KDE libraries are GPL’d as well.
I also believe that KDE could use some cleaning up. Only to assure that the UI is consistent and hopefully more optimized so it can run faster. I’m surely not saying that they should cut out features, just make sure that the code is cleaned out to strip away things that aren’t needed or not used. Anyway, that’s just IMHO.
2005-12-13 4:23 pm
Go to top500.org, then tell us linux is just a hobbyist OS.
For a hobbyist os, it runs on some of the best supercomputers of the world. Truly hobbyist, we can all afford those supercomputers.
OS market isn’t just about office people. An OS isn’t anymore just for hobbyists when it’s used for cricital tasks like that.
“Arguing by reductio-ad-absurdum is a known logical fallacy. Yet you do it.”…
Reductio ad absurdum is a perfectly valid method of argument, it’s not a logical fallacy at all. He probably was mistaken because he saw it listed on a logical fallacy website. Those websites list it because it’s actually an argument AGAINST a logical fallacy; it’s a form of proof-by-contradiction.
You take the person’s argument to its logical extreme and show that because of the absurdity of that extreme, that it must be wrong. The fact that the person’s logic allows it to be taken to that extreme means that it’s flawed. A proper logical argument will account for that and place limits that prevent extremes from being logically valid in their system.
-njyoder
2005-12-13 4:21 pm
> Reductio ad absurdum is a perfectly valid method
> of argument, it’s not a logical fallacy at all.
Which is rather interesting isn’t it? You’d think the real Linus Torvalds, computer science graduate, would know better. After all, logic classes are an essential part of a CSci curriculum. Again, it sounds like more evidence that this is probably not the real Linus. Resorting to big buzz words to try to intimidate others, and not even knowing what those buzz words really mean.
When will the “leaders” of open source get it? For open source to take off, they need to stop bickering and start working together.
The more that leaders of various large influential OSS projects publicly belittle others, the more they are blown off as immature children. They get the, “Thats nice, go run along and play now.” Much like when Eric Raymond publically posted the ridiculous response to the Microsoft job recruiter, this is yet another black eye to the Open Source Community as a whole.
In other news, it seems like the trend recently is for the KDE lovers to bash gnome to no end. Kurt P certainly ripped novell a new one with his opinion piece full of lies and deciet on linuxtoday:
If you don’t like gnome, fine. If you like to spread fud, post on /. don’t make the whole community look bad. Thanks
Quoting Nat Friedman replying to Linus:
“We need Linux to grow up if we’re going to make Linux on the desktop a success. Let’s have a grown-up discussion. If I worked for Microsoft I’d be very happy to see you throwing pejoratives around like that on this list.”
LMMFAO….. The folks at Microsoft probably sent Linus flowers and candy, with a note thanking him for his support.
In future news:
Torvalds joins Microsoft Research and Development.
This is probably the biggest KDE-Gnome flamewar ever!
Thom I humbly ask you pretty please, save this flamewar in a very secure server with some paper copies so that future generations of archilogists can see how in the year 2005 B.C.S. (Before Common Sense) the fanboyism reached the Ultima© Flama®!
YeS, Quintuple, hypEr n0va, Alucard, Shazam, Tripla, Songoku, ZenPowerRangerPlusMegaTransform.
YYYYYEEEEESSSSSS!11!11!!!twentythree!!11!11!!!!!
(Note to you my friend future archologist, back in this era we were poor but very happy, remember this and apply it to your own life in you admirable new world)
-
2005-12-13 4:41 pm
I have to agree with Torvalds on something. KDE is without a doubt a better experience than GNOME. Not that GNOME is really bad, I just find myself always going back to KDE. It just seems more polished, seems to run faster, and just has more features that I like.
KDE vs GNOME – they are both being actively developed and made suitable for at least the people making them so good to them both.
I use fluxbox (on the rare occasion I actually fire up X) and dislike both KDE and GNOME but I’m not going to go and bitch to people about what I don’t like and tell them to use fluxbox. Likewise I use FreeBSD instead of linux but I don’t go and tell everyone to use that and not linux.
Sorry Linus but truly bad idea saying something like that, your reputation grows worse by all of your bad moves not better. Just because you wrote the first linux kernel and work on it with a small group of people doesn’t mean you can be an ass to hardworking people like those working on GNOME.
2005-12-13 5:09 pm
> Linus is a UNIX kernel hacker.
> GNOME is for average desktop users.
> Linus finds GNOME doesn’t suit him.
And yet KDE does? I’ve always found KDE to be much “less technically demanding” than Gnome. So that logic doesn’t work very well. Gnome is more for power users than KDE is. Gnome is basically infinately customizable. But customizing it required digging around at a fairly low level. KDE isn’t nearly as customizable. But the customizations you can do are easier because they can all bew done from the KDE control panels.
2005-12-13 5:11 pm
> Gnome is more for power users than KDE is.
Strange that every power user I know finds GNOME scary (including me and Linus and many others). So what ? Either GNOME is for the idiot users amongst us or for the power users. Your “power users” sentence totally contradicts to the “ordinary users” stuff that GNOME aims to target.
2005-12-13 5:18 pm
> Strange that every power user I know finds GNOME
> scary (including me and Linus and many others).
I don’t use either Gnome or KDE is my regular desktop. Typically I use fluxbox. Since mostly I just want the ability to manage multiple windows, and have the window manager stay out of my way.
When it comes to toolkit issues though, Gtk is a vastly superior toolkit to Qt. And yes, I have programmed in both. Qt has some very bad design flaws. And Gtk is the only one of the major GUI toolkits for Windows that actually takes advantage of standard C++… Hey Qt people? Every heard of something called “namespaces”? Maybe you should look at gtkmm and learn what they are, and how they are your friend… Oh, and while you are at it, adding proprietary extensions to C++ that requires a special pre-processor is BAD.
-
2005-12-13 5:18 pmdark child
I am not sure you are talking about the same KDE as everyone else. I use both desktops on a regular basis and of the two KDE is the one that can be customised a lot more.
Both are good DEs, but GNOME seems to have gone downhill since the 2.x release. GNOME 1.4 was one of the best ever GNOME releases and I wish GNOME had continued in that tradition.
2005-12-13 7:44 pmdylansmrjones
Yeah Gnome 1.x was nice.
Gnome2 is slightly annoying, and I didn’t like the changes from 2.6 to 2.8 – definitely going too far, as Jeff Waugh admitted.
The Gnome desk top has gone down hill since 1.4. Everything that was cool in 1.4 in the way of customizing your environment has gone away. It’s soo dumbed down that it’s annoying to use. Windows is more intuitive now. I’ve switched to KDE and haven’t looked back. Gnome 1.4 was better, but against gnome 2.x, KDE rules.
Linus told the same truth that many have been speaking since GNOME 2.0 came out. Forcing spatial file management on users, as well as reversed save/open dialogs does not improve usability. Hiding the ability to have the window manager act left handed (with close/maximize/minimize buttons on the left of the window manager rather than the right) does not improve usability. Horrid file dialogs do not improve usability. All Linus did was reiterate facts already well known and discussed.
Good to see a developer doing something about it.
Personally I prefer Gnome, but there’s no doubt it needs get back on track.
Since 2.6 It’s been going extremely downhill.
Torvalds aren’t saying it the nice way – but then, the nice way is never effective.
The gnome simplicity has gone WAY to far. Not that I want the stupid complexity of KDE with absolutely no consistency in UI and mediocre drag’n’drop.
It’s time for K-nome to arrive.
-
-
2005-12-13 5:24 pm
Not only that, but he made it clear he has never used Gtk. Because Gtk *is* object oriented. (Hint to the original poster: It is possible to do object oriented programming in C).
Oh, and if he doesn’t want to… There is always gtkmm, which is vastly more object oriented than Qt is. It actually takes advantage of C++ features and doesn’t resort to old C tricks like macros that break object orientation in evil ways.
2005-12-13 5:30 pm
> Not only that, but he made it clear he has never used
> Gtk. Because Gtk *is* object oriented. (Hint to the
> original poster: It is possible to do object oriented
> programming in C).
I contributed to GNOME for some years but then, GTK’s great OO approach doesnt help if half of the people use the OO approach and others not. Some people simply call function calls rather than referencing some objects. What benefits does GTK’s great OO approach habe if it’s used half by apps, if people still keep programming the good old ‘calling functions’ and ‘calling functions to alter attributes’ way, what benefits does it have that many bindings or other things don’t implement these things nicely enough ?
Looking at this screenshot gives a great example that the so called great OO approach has miserabely failed. There is not even one common Toolbar object that people can use – and use in an unaltered way so they look consistent.
Show me one KDE application that has a Toolbar which looks differently than other Toolbars used in KDE.
Only one!
2005-12-13 5:51 pm
“There is not even one common Toolbar object that people can use – and use in an unaltered way so they look consistent. ”
First of all, this has absolutely nothing to do with object oriented programming.
Second, yes there is. There is a complete set of stock icons that come with Gtk, and if you change the theme, those stock icons will be changed too. If developers use those stock icons, their apps will pick up the Gtk theme.
Of course, you can’t force developers to use stock icons in Gtk. But you can’t force them to in Qt either. In otherwords, there is no toolkit that can stop developers from designing back UIs.
2005-12-13 5:57 pm
> First of all, this has absolutely nothing to do with object oriented programming.
It has.
> Second, yes there is. There is a complete set of stock icons that come with Gtk, and
> if you change the theme, those stock icons will be changed too. If developers use those
> stock icons, their apps will pick up the Gtk theme.
I don’t speak about icons dude – and I give a flying f–k about them too.
I speak about the code, object oriented toolbars (containing toolbar editor, and other stuff) behave similar. If I inherit that toolbar object in all the apps that require a toolbar then they all behave consistent. GNOME is NOT doing this – everyone is freaking hacking together their own toolbar, tweaking around with attributes and other shit. No toolbar looks like the other.
Get some brainz before talking with me and if you happen to not get anything from what I write then stop replying and stop wasting my time.
2005-12-13 6:01 pmdylansmrjones
The toolbars in different gnome applications have similar behaviour but different content.
Your statements are false.
The look of toolbars has nothing to do with object oriented programming.
The look of toolbars in gnome are very similar across applications, though the contents differ. But behaviour is similar in all of them.
You don’t use Gnome apparently.
Take a look at gedit, gnumeric, openoffice, thunderbird, firefox, mozilla, epiphany, bluefish and you’ll see that these applications with some even being non-gnomic actually looks and behaves the same way.
The content is different, but basic behaviour is identical.
2005-12-13 6:08 pm
> The toolbars in different gnome applications have
> similar behaviour but different content.
No, that’s wrong.
First of all, you do understand the difference betwen ‘content’ and ‘code’ ?
Content is the shit shown on the toolbar.
But I speak about the ‘code’ and their attributes how the toolbar looks once the code for generating it has been processed.
> The look of toolbars has nothing to do with object oriented programming.
The look of the toolbar has a lot to do with programming. Again it doesn’t matter what ‘symbols’ are shown in the toolbar, what I speak about is how the toolbar looks and behaves.
So please again from the screenshot:
Now please have a look at that damn toolbars dude.
a) some toolbars have a drag handle (the small thing on the left side where you can untie the toolbar)
b) some toolbars have icons and text while others not
c) some toolbars are higher than others.
AGAIN I DONT SPEAK ABOUT ICONS or the godamn images shown.
If I use common object oriented approach I would have a custom toolbar class somewhere in my f–king library, that has support for showing icons only, icons and text, make the toolbar show smaller or bigger images, or simply edit the toolbar.
GNOME has many ways doing a toolbar dude, one from libbonoboui, one from libgnomeui and the new approach in GTK+
> The look of toolbars in gnome are very similar across
> applications, though the contents differ. But
> behaviour is similar in all of them.
No they are not, please look at the screenshot a bit closer.
> You don’t use Gnome apparently.
I do and hell I spent my f–kign past 6 years telling clueeless GNOME developers about this issue.
> Take a look at gedit, gnumeric, openoffice,
> thunderbird, firefox, mozilla, epiphany, bluefish
> and you’ll see that these applications with some
> even being non-gnomic actually looks and behaves
> the same way.
They are not.
> The content is different, but basic behaviour is identical.
No, it’s not.
2005-12-13 6:47 pm
Omg is this guy still crying about the toolbar issue. Wow it is impossible to have any gnome related thread without this guy crying about some moot issue.
Look nobody cares. Shut up. This has been disputed three ways to sundays. Different applications = different toolbars. Different application developers = different toolbars. What the hell is so complicated about that.
So are you gonna keep bsing that your a developer even though you seemingly have no idea what a toolkit is, and that the developer has no obligation in using a toolkit. Im pretty sure you have no clue whatsoever.
“a) some toolbars have a drag handle (the small thing on the left side where you can untie the toolbar)”
All toolbars have a drag handle…..except galaxy. I have been a gnome user for about a year and never heard of galaxy. I have looked on gnome-files and googled it, I has been 2 hard for me to find it. Conclusion: at the most its a 3rd party application. What does galaxy do anyways. (it might be useful ^^)
“b) some toolbars have icons and text while others not”
hey dumbass, did u realize that the the icons with text are on the applications that have BIGGER icons. Would you understand why developers would want bigger icons then smaller ones for some applications. Would you think that some applications have a WEALTH load more commonly used icons then other application. Could it be possible. Noway!! How could it be possible that users will need more icons to do something in AbiWord compared to gedit. Well why dont we do the kde thing, where they scrunch over 5 icons over to the left and make them tiny as hell? As a person who prefers gnome, I will say no.
“c) some toolbars are higher than others.”
What the hell does that mean. Apart from your an idiot?
I hope you aint crying about toolbar size, because I hope u know that bigger icons = larger toobars.
Going back to Linus. Ill say its impossible to have a war without soldiers on either side. Linus chose kde, and his words show that hes up to defend his choice. Thats good for him. Everyone needs a little of that.
2005-12-13 8:35 pmdylansmrjones
I do understand the difference between content and code, and we agree on the definition. If people cannot see the difference they’ll have a hard time understanding how things work or don’t work.
The look and behaviour is pretty much the same for those applications. Whether they have a handle or not means nothing. It’s just a different value for a certain attribute.
It’s working the way it’s supposed to. You’re making an issue of a non-issue.
And yes. Thunderbird, Firefox, Epiphany, Mozilla, Bluefish, gedit, gnumeric, Totem etc. look and behave similar to each other in regard to toolbars.
You can say “no” as much as you want.
As a user I haven’t met any inconsistency so far in modern Gnome apps (having used Gnome since late 1999).
Different height is a non-issue. It’s just an attribute and is not a part of behaviour.
The same goes for handles.
GTK+ has a common class for toolbars, and look and behaviour is controlled via attributes and events. Just like in all other reasonably modern tool kits.
2005-12-13 6:23 pm
I got a better idea. Learn how to spell and talk properly, and make you will start looking like you have a clue what you are talking about. It’s clear you don’t.
And in case you didn’t notice, you can do inheritance in Gtk. But I bet you are just too lame to actually have taken the time to figure out how.
2005-12-13 6:27 pm
2005-12-13 6:33 pmSimba
“Exactly, you *can* inherit, but you are not forced. The mess we see today. Above screenshot is the best example how much it fails.”
Dude, you obviously don’t understand the Gtk structure. YES, you do have to inherit. And you seem to be hung up on the idea of inheritance. If you are subclassing a toolbar class to create your toolbar, you are almost certainly doing something wrong. a toolbar class is almost never a good candidate for subclassing since you almost never want to change the default behavior. Repeat the mantra “Program to interfaces. Not implementations”. Get out of the inheritance trap before it bites you.
And in Qt, there is nothing forcing me to use a standard toolbar either. I am 100% free to create a god-awful mess of a toolbar if I want to. I can use non-standard icons, place buttons in non-standard locations, etc.
2005-12-13 6:38 pm
> If you are subclassing a toolbar class to create your
> toolbar, you are almost certainly doing something
> wrong.
Exactly. So please tell everyone (including me) why Evince has a Toolbar editor and Yelp for example not. Tell everyone of us why I can change the Toolbar using “Toolbar & Menu” capplet but I can’t change the one from Gnumeric.
Go ahead explaining. I thought GNOME was all about consistency and clean look. But yet the shit doesn’t look that clean because all the Toolbars are behaving differently.
Of course you can subclass KDE’s toolbars too, no doubt but why should you want that ? The toolbar contain all the stuff needed and every KDE app inherits the default toolbar object and only alters the accelerators used.
So why does KDE get it right and GNOME not ? Why do all the GNOME loons talk about HIG and GNOME and consistency in one sentence but still fail with it while KDE (3 times bigger than GNOME, get’s this stuff right) ?
2005-12-13 6:44 pm
“Go ahead explaining. I thought GNOME was all about consistency and clean look. But yet the shit doesn’t look that clean because all the Toolbars are behaving differently.”
Again, you can’t force programmers to write good UIs. And Gnome toolbars do not behave differently. I don’t see what the big deal is. You add a toolbar in Glade, and you drop in the stock buttons you need.
“Of course you can subclass KDE’s toolbars too, no doubt but why should you want that ? The toolbar contain all the stuff needed and every KDE app inherits the default toolbar object and only alters the accelerators used.”
You don’t have to subclass the toolbars to do stupid things with them, like use non-standard icons that won’t pick up the the theme, etc. you can do stupid things with Qt toolbars just as easily as you can with Gtk toolbards.
Oh, and since you wanted an example of a truly horrible Qt application, I will give you one. Skype. Skype’s UI is a f–king mess.
2005-12-13 6:49 pm
> Again, you can’t force programmers to write good UIs.
> And Gnome toolbars do not behave differently. I don’t
> see what the big deal is. You add a toolbar in Glade,
> and you drop in the stock buttons you need.
Why not ? I see big issues into that. And how comes KDE doesn’t have these issues ? There is no KDE application that comes into my mind that uses a different toolbar object than the default one. So why are the GNOME developers incapable doing the same ?
So again, please explain why one toolbar has a drag handle, the other has icons only, the other icons and text, why is the one toolbar a few pixels higher than others, why do they still use deprecated UI mechanisms from gnomeUI and bonoboUI rather than having switch to GTK+, why does tools like Evince and Epiphany have a toolbar editor while the remaining rest of the GNOME apps don’t ?
I don’t see that mess with KDE really and your sentence that you can’t force everyone to do the same is quite a bad excuse demonstrating that there is something wrong with the framework that GNOME provides. Why does it work with such a big project like KDE which is by means three times bigger project.
I mean, and you probably agree that the toolbar issue is just a small issue compared to all the other issues (like the one from torvalds) found in GNOME. It starts with basic stuff such as printing, goes on with toolbar issues such as conceptual issues and and and.
You hopefully get the hint here. GNOME developers are generating a lot of own work where it’s not required. Things could have been changed for the better in less amount of time and much frustrations could have been avoided by doing so.
But they didn’t. So Torvalds compliant is justified and correct.
2005-12-13 5:57 pmdylansmrjones
Different applications have of course different toolbars.
The gnome toolbars look similar, yet are different because the applications are solving different tasks.
Would I expect a text editor to have the same buttons on the toolbar as a file windows or a browser window or a spreadsheet application?
NOOOOOOOOOOOOOOO.. I would expect a text editor to have icons relevant to text editing, and a spreadsheet window to have icons relevant to spreadsheet jobs.
The pictures at imageshack shows just how Gnome apps are fitting to their task. And it looks pretty much the same way or all other platforms.
There is no platform, not even KDE where a mail application has a toolbar which is completely common to the one in a spreadsheet.
Different contents in the toolbar yes. A common class for toolbar yes. Gnome has both. As has KDE, Mac, Windows, Amiga OS, MorphOS, Haiku-OS, Zeta, BeOS, SkyOS and etc.
2005-12-13 5:58 pm
No, you are wrong too, please read:
To get some enlightenment.
2005-12-13 7:48 pmdylansmrjones
Aaahh shut up. I already that and replied to that you f***ing moron!
I’m right and you’re wrong. You claim that toolbars are not common in Gnome – but hey they are.
Seems to me you don’t know what you’re trying to say.
Are you complaining about the look or the basic behaviour? The look is visual – behaviour is what happens when dragging, dropping and clicking and such.
Look at the screenshots posted from ImageShack. They show how identical the toolbars are.
As a daily user of Gnome and a coder as well, I’m pretty sure I know more of Gnome 2.10’s behaviour than you do.
2005-12-13 5:31 pmdylansmrjones
Whatever..
KDE is too inconsistent. Gnome2 is too simplified.
A blend of KDE, Gnome2 and Gnome1 would be better.
An object oriented approach is always good in regard to GUI. It might not be good in regard to very small CLI programs, but for a GUI OOP is the right choice.
The Gnome simplification has gone too far, but the mess in KDE isn’t the option.
I respect him for his work and what he has done. But this doesn’t really matter whatever his preference. Or that I should use Flux Box, XFCE, KDE or Gnome over another! Or hell whats that’s one that mimics windows really well.
I prefer GNOME because it’s easy to me and I have been using it forever. My only KDE expierence is Kanotix and I find it harder to customize when the default is that big’ol’bar at the bottom.
Linus prefers KDE…great! Glad to know he likes something. Can we all put our efforts into making all software free and awsome and what not now? Then argue which one is better D:
Glad I am at osnews posting and not /. I mean jeese they are at 687 comments in that stupid BBS format making it impossible to read.
2005-12-13 5:33 pmdylansmrjones
It can also be overdone.
A windows should show exactly what you need. No more, no less.
KDE shows too much, Gnome shows too little.
In general Gnome misses the “Advanced” option.
The wise choose wisely.
Gnome has:
* A freakin’ slow window manager called Metacity, and it’s a huge pile of ##.
* A toolkit that is seriously suffering from performance problems, and has for too long.
* A terminal application that is so slow it’s almost unusable.
* Exaggerated simplicity everywhere.
* Crap like gconf.
* A tightening relationship to diseases like Mono/C#.
Steer clear, like Linus does.
Linus is a normal guy. a funny one at that. I’ve not read many of his emails but of the few things I have I always chuckle.
The funny things about his comments tho are not that they are off. Most if not all _are_ dead on.
If you can’t do something *is* that usability? There are numerous ways of defining usability. I personally use the approach, Can I use it for what I need to? Can I do what I need to do easily?
Gnome takes this backwards it appears.
“Can They do what they need to do easily?” and forget about “Can they do what they need to do?”
Sure KDE has TONS of options that I’ve never touched and never will. I never thought I’d change the window buttons. But I have. I dropped the maximize button and swapped the locations of the close and minimize buttons. Why? for _me_ it’s more usable and safe. When you got a mouse that likes to go out of control sometimes right when your going to click a button and you end up closing out the program. That’s not good.
Should KDE Clean up these dialogs by removing the ones no one uses? I’d prefer they didn’t.
Would a normal user want to do what I did to my title bar buttons? No.. if they removed this I’d be rather upset.
Lets take a different look at things.
Can you go to far if you:
A) Strive for Simplicity
B) Strive for Features
First lets make something clear. How often are you going to be configuring something? Not very often. So are lots of configuration options bad? Well looking in yet another way. When your actually using the WM, are you wishing you could change something so you can work faster and more efficiently? If so then no configuration options are most definitely _not_ bad.
When I work in windows I really wish you could use the scroll button on mice like I can in linux.
click it to paste. Select windows without bringing them forward. change windows and various other things.
This is actually how I get more users interested in linux. we got on the topic and I say I can’t work well in windows and I start telling them how I work faster. All of these are things I do every do on an hourly basis. Hourly basis operations like these are _far_ more important to me any anyone I’ve ever talked to. than any configuration dialog. But I could not have it my way.. and you, yours if not for these options in a configuration dialog.
The beauty of Linux and Open Source solutions is general is; if you don’t like the way it works you have choice in what other options are available. Just because you think a desktop is too simple doesn’t mean someone else has to think your way. It works the same with development politics and teams. If you don’t like the way a group is working you don’t have to use there software.
2005-12-13 5:38 pm
> The beauty of Linux and Open Source solutions is
> general is; if you don’t like the way it works you
> have choice in what other options are available.
This sentence is NOT VALID anymore. There is no choice anymore. It was a few years back but nowadays the shares have been divided between KDE, GNOME, XFCE.
…in their own way
I find kde too bright and flashy, and gnome too grey, but the icons are nicer. I don’t like spatial nautilus, but its easy to change to ‘browser’ mode. What else? Kde has a nicer clock and k3b, but, you know.. big deal. I no sooner start using one but then begin missing the other. Its a lot like trying to find the perfect distro; many of us, me especially, are too restless. When will it ever end?
I envy Linus; he’s found his perfect DE.
This is one of the funniest threads I’ve seen, and Linus only made three posts!
Maybe Linus thinks this whole Portland dog’s breakfast thing is as distasteful as I think it is. Just cut to the chase, let’s get something that works and let’s stop arsing about with stuff that isn’t possible. You then got all the politically correct posts after Linus’ saying ‘let’s work together!’ etc. etc.
I prefer Gnome. I’m not a nazi. I am offended by this dialogue. As a soon to switch Mac user, I have to say that similarities are there between Mac OS X and GNOME. Easy, clean interace, but Mac users are not dumb people, nor are GNOME users!
I would suggest mr Linus to be on prozac for some weeks.
Maybe he would be less offensive, while retaining his own preferences like he has the right to do, as do I and everybody.
-
-
2005-12-14 9:46 amPasha
You’re right : OSX is an OS while Gnome is a GUI.
I was referring to the ‘ease of use’ when compared to the cluttered KDE interface. OS X is clean and so is GNOME. That’s what I was talking about. OS X Tiger ‘Dashboards’ resemble GNOME desklets. They sure work different and are different, but as a user experience they look both clean and easy, and similar.
-
2005-12-14 9:54 amPasha
No. I can read. Maybe you’re not so well educated :
Well i do not feel an idiot because I use GNOME or because I prefer to use a GUI instead of a terminal.
I have the right to feel offended by these words, and you should better connect your brain before speak.
2005-12-14 2:33 pm
No. I can read. Maybe you’re not so well educated :
No you can’t, and your usage of the english language shows that you are probably less educated than you think. (English isn’t my native language either.) i do not feel an idiot because I use GNOME or because I prefer to use a GUI instead of a terminal.
I have the right to feel offended by these words, and you should better connect your brain before speak.
Ok, smartass. Where in the quote above does he state that those who use gnome are idiots? Nowhere. He speaks of a mindset among the gnome-developers, that makes them treat their users as idiots. A HUGE difference. You need to brush up on your reading comprehension before you run around and get offended by everything. In fact, I find you are quite insulting yourself, since you can’t be arsed to find out what someone actually is saying before you jump them. Not that I expected a zealot do something that complicated, but it would have been nice to be proven wrong on that one.
Who cares what linus thinks about desktop environments? He’s a kernel hacker, does it make him an expert of desktop environments? Of course not. What if he said to drink coke instead of pepsi? Would you do it?
I use gnome and won’t switch back to KDE because linus said so. It’s a personnal thing.
Are all the other DE/WM complete crap? No they aren’t, they simply have different supporters and contributers. The more the better if you ask me. They can steal ideas from each other and they all benefit.
Firstly, If Linus doesn’t care about Gnome that much, WHY is he posting on the mail.GNOME.org forums! *rolls eyes*
Secondly, I would be 100% happier putting somone on my Solaris machine running JDE (Gnome based) then I would running KDE… Sure, KDE is VERY NICE, but it is the other side of the coin.. too many options.
Mr Torvalds, some of us really LIKE Gnome, sorry
Oh right, so this is why OSnews went down with the “Dang” message. Without reading 345 posts I KNOW what it’s about, so thats why i’m not doing to.
To claim what Linus always says is the holy grail is stupid, if he like KDE more good for him. Mocking your own OS like that just because he dont like GNOME is childish. Go back to coding the kernel Linus.
I do agree his opinion about the file dialog though
“Same with the file dialog. Apparently it’s too “confusing” to let users
just type the filename. So gnome forces you to do the icon selection
thing, never mind that it’s a million times slower.
”
Direct link for this comment Registered users can bookmark useful comments
I don’t, just do ctrl-L and you can type whatever you like. So Linus => RTFM!
I am not going to read through all 360+ posts right now, but i just wanted to mention that i thought this was the point? To get the so-called “Idiots” from the windows world to switch to linux? That is why the race to hide complexity and make the interface less intimadating, its for users who were use to windows.
To me its an obvious choice, if you like simple and clean, use Gnome. If you dont want to be scared with features and the underpinings of your OS/GUI use Gnome.
For everyone else, there is KDE and a host of other windows managers such as AfterStep(my favorite) GnuStep, enlightnment. And for true minimalists there is black box (and the like)
I see no problem with Linus’ statement. He is just stating the obvious.
since you almost never want to change the default behavior.
And it only shows you are totally clueless of what he is saying. If you look at the example given it shows three different default behaviors. A proper class and inheritance structure would not allow this.
I am 100% free to create a god-awful mess of a toolbar if I want to. I can use non-standard icons, place buttons in non-standard locations, etc.
And it don’t have anything at all to do with this case, they would still look and behave like the other toolbars as they use the same toolbar class. The look and placement of the icons are irrelevant.
2005-12-13 7:07 pm
“And it only shows you are totally clueless of what he is saying. If you look at the example given it shows three different default behaviors. A proper class and inheritance structure would not allow this.”
Bullshit. You don’t know what a proper class and inheritance structure is do you? A decent class is loosely coupled. Again, “program to interfaces. Not implementations” Programming to concrete implementations is bad. It results in an explosion of specialized derived classes. That is BAD. If the default toolbar doesn’t work for me, I should NOT have to subclass it to change the icons, or change the order. In fact, the buttons themselves have NO BUSINESS being part of the toolbar class. That results in a highly specialized class that is not reusable.
Repeat the mantra: Inheritance is bad. Composition is good. A tightly coupled class structure like you suggest means that things can’t be built through composition. And that leaves you with having to subclass. And results in an explosion of highly specialized derived classes.
Please read a good book on design patterns.
2005-12-13 7:50 pmdylansmrjones
Of course a proper class and inheritance structure would allow such a thing. That’s the whole f***ing idea of class and inheritance.
I did a Debian net install a few times, and I was amazed at how many Gnome programs and libraries had to be downloaded, as opposed to the KDE programs and libraries. The Gnome stuff took about 40 minutes to download, and the KDE stuff took about 10 minutes. Yet, KDE is more powerful and configurable and more feature rich than Gnome, by an order of magnitude. Plus, KDE manages to be faster and less memory intensive than Gnome. Go figure.
This is all an indication of library dependency labirynth and bad internal design on Gnome’s part. You’d think that with feature deprication, and a nice, intuitive, simplistic interface, the guts of Gnome would be simple and light. But it’s not. It’s apparently a bloated, complex mess.
Then there is Xfce, which is light and fast and still feature rich, and uses GTK and a clean, simple interface. I look at Xfce as Gnome done right. It’s everything that Gnome should be. It has the best features that Gnome has (namely the simple, clean, easy to use interface guidlines), but lacks Gnomes weaknesses (namely structural bloat, key features depricated, resource hog, lack of key configurablity).
Maybe Linus’ post was flamebait, but at least it led to intelligent discussion in response on the mailing list. I have never seen a forum where one can bring up the subject Gnome’s “feature vs usability” design intent without being flamed to high hell by self-righteous Gnome users. I’m not singling Gnome out for this, since certainly the KDE camp has more than it’s share of equally self-righteous zealots, but it is nice to see a rational discussion follow because that is probably the single biggest thing that irks me about Gnome.
Frankly, I share Linus’ opinion, I’ve always felt that Gnome’s superior usability was simply a shield to hide behind when it came to functionality or configurability. Is KDE perfect? No, and KDE has even acknowledged this as being a topic of focus for 4.0, but having said that, I’d much rather dig through an options list to find the one I want rather than find that the option didn’t exist at all.
Yet I’ll admit that’s strictly my personal preference. Do I think lesser of people that don’t share that opinion? Of course not, I firmly believe both DE’s are integral to the success of desktop linux because they are so different. I’m even willing to admit that because of my background (cut my teeth using a CP/M-based Osborne as my first computer before climbing the ladder from PC-DOS 1.0 through Windows XP with all of the incarnations in between), I probably take things for granted that not everyone else would. I am unable to put myself in the position of less-experienced computer users, something I realize every time I help someone my office with a Windows or system problem, so I’m willing to realize that maybe my experience, my perception and my choice of what works best isn’t necessarily applicable to everyone.
Personally I can’t get comfortable with Gnome, I feel like it’s looking down on me when I try to do things a certain way, I can almost imagine it tsk-tsk’ing in the background. And it seems to me that as many people defend Gnome’s usability, there are a considerable amount that question or dislike it. That makes it a valid topic for intelligent discussion (how can you boast about a desktop for “users” if you invalidate other user’s opinions that differ from your own?). Yet all I ever see if needless flaming (“KDE sucks!” “KDE fanbois get a life!” “Gnome rulz, you’re 2 stupid!”), which accomplishes little, any time the subject it brought up and does nothing to help sway opinion or allow others to consider alternative points of view.
(And again, let me stress, I’m not taking the high-road and saying KDE doesn’t have it’s share of flamers, because it certainly does and I find it equally counter-productive)
Both desktops complement each other, in that they address things in ways that are almost diametrically opposed. To me that means users don’t have to compromise, chances are you’ll prefer one or the other, you don’t have to sacrifice. If Gnome suddenly became the only desktop choice on Linux, I’d probably re-evalutate whether Linux was acceptable to me as a day-to-day platform. But by the same token, if KDE dominated and was the only choice, I’m not sure I’d like that either because invariably the product would suffer and there would likely be little incentive to truly innovate or improve (as always seems to happen). I much prefer having Gnome as an available option, even if I may not be using it today.
The “desktop war” can be constructive if both sides can accept differences of opinion, look at areas where they may be weak and strive to improve, and continue building upon the co-operative efforts to ensure interoperability (which, really, is the most important thing).
But useless flamewars just force both sides to hide behind their own rhetoric and cliches, attacking the other side while ignoring their own issues. No progress can be made that way.
For crying out loud, this isn’t Highlander. There can be, and should be, more than only one. So good on you Linus for at least spurring intelligent debate, even if that wasn’t your intent.
You want to know why it is that most of us out here who are reading this on their Windows XP machines haven’t switched to Linux yet? Linux is a confusing, tangled mess of techno bable and complexity that the average Jane/Joe doesn’t want to think about. Here’s a recent conversation I had with a neighbor:
“So Mrs. Jones, you’ve decided to take the plunge and switch to Linux and get Windows 98 off your machine, that’s great! Let’s see you will need to decide which “distro” (new word for the uninitiated) you would like from a list that’s a mile long. Oh, I’m sorry, you’re a little confused?” You go on and explain the whole “open source” thing to her as best you can, keeping the language as non-geek as possible (which is a feat all on it’s own) and she finally says to you “just pick one for me.” So, you do and then you ask her which window manager she wants and here you go again explaining the pros/cons of this wierd idea to her and she says, “Sounds like a mess to me….thanks for your time, goodbye” and hangs up the phone.?”
Back to work now geek!
2005-12-13 11:27 pm
?” ”
I f–king could care LESS if Joe Sixpack use or not linux. Linux is about freedom, not taking over the computer world.
Joe got his Apple Mac. I use my linux. Who cares ?
I f–k the guys who needs a linux that do all the things automatically for your little ass. You want a gay os, use OSX and don’t come f–king with us.
Free software is also freedom of choice. Not crappy GUI that tries to think for you.
The reason the hurd is alive is about the freedom of the user, to give more freedom to users with a new architecture towards a more user land based system that don’t need kernel mode for all things. Why we should, FFS, destroy the liberty the free software gives us, to make a Joe Sixpack standard GUI like MacOSX ? if you are not happy with linux, just use windows or mac osx. Or build your new unix system like apple did. You already got some choice, why bother with linux if you are not happy with it ?
I aggree that the gnome Interface Design is to conservative, why do OS Devs always reject USer wishes and ideas?
Apple didnt and have big success with aqua(give me 1000€ and i join in), just copy any GUI toy you can and you get an wider userbase.
But like the KDE guys said, we dont need any/our users to let KDE exist.
I use Gnome, mainly because the QT rendering sucks and hurts my eyes
I’m scared to read anything on here. The words that were stated tend to be fightin words in the community, so I’m going to stay out of it on which is better. I personally prefer KDE (although it still needs more spit & polish) because it’s close to Windows. Not in ease of use, just location and functionality. BASH also tends to get the job done, although I’m not as skilled at it yet. I can do configure; make; make config and edit with VIM, restart services and mkdir rm and cp files all over /. I do wish KDE wasn’t so generically looking, but since I don’t contrib, I don’t get a say.
Umh, KDE lacks screensavers out of the box? I don’t know what kind of box are you using, but AFAIK there’s been screensavers in KDE as far as I’ve been using it. And if you have kscreensaver-package installed, you can also use xscreensaver screensavers.
So, I’d say your problem has nothing to do with KDE but with your distribution.
I just thought I’d say something that I haven’t seen mentioned yet. Linus’s original gripe was that he wanted to configure his mouse buttons in a certain way in GNOME but found that it wasn’t possible, and for this reason prefers KDE. Couldn’t he have just used another WM instead of the default (Metacity).
(Note: I don’t use either, as I find them both bloated. I’m so glad we have a choice of WM/DE)
Today just before i read this article i installed Ubuntu and decided to test the KDE version (aka. kUbuntu). I was quite impressed. Though I am a Gnome user since Gnome 1.4, I found KDE to be both fast and “user”friendly. (Userfriendly = a bit more options then I am used to but nevertheless userfriendly.)
My point:
Use what works for you! Don’t just listen to everybody else, try it and make up your OWN mind.
Regards.
“If you think your users are idiots, only idiots will use it. I don’t use Gnome, because in striving to be simple, it has long since reached the point where it simply doesn’t do what I need it to do.”
That may be so, but if we could target the “idiot” type of user, the Linux desktop user base would increase significantly.
You have to realize that asking what DE is best for Linux users, and what DE is best for Linux, currently are two very different questions.
It is just as true that if you design for the elite, only the elite will use it. The difference is, that people that are not idiots will be able to switch to KDE by themselves, the “idiots” on the other hand will not be able to switch from KDE to Gnome.
So perhaps Mr Torvalds (if he actually wrote this) should leave usability to people that knows more about people than computers.
+1 agree!
I think, Gnome does a great contribution to Free Software, because they strive to make it simple, and the best of their Ideas will be carried on by others and benefit tp all like that.
What I think really useful would be links to a comparision of those two with the fokus on the people to whom certain features appeal.
Then it would be far easier to decide which one to recommend to the different kinds of newcomers.
Wishes,
Arne | https://www.osnews.com/story/12956/torvalds-use-kde/comment-page-2/ | CC-MAIN-2022-33 | refinedweb | 14,547 | 73.47 |
Closed Bug 141369 Opened 18 years ago Closed 17 years ago
Support IMAP4 IDLE command (RFC 2177)
Categories
(MailNews Core :: Networking: IMAP, enhancement)
Tracking
(Not tracked)
People
(Reporter: moz-bugz, Assigned: Bienvenu)
Details
(Keywords: helpwanted, Whiteboard: parity-oe)
Attachments
(1 file, 1 obsolete file)
From Bugzilla Helper: User-Agent: Mozilla/5.0 (Windows; U; Windows NT 5.0; en-US; rv:1.0rc1) Gecko/20020417 BuildID: 2002041711 Mozilla mail does not seem to use the IMAP IDLE extension specified by RFC 2177. Would be very nice to have and should not be too complicated to implement. Reproducible: Always Steps to Reproduce: 1. add imap account with an IDLE capable imap server (such as cyrus) 2. open inbox 3. send mail 4. wait Actual Results: nothing happens till the "check for new messeges every # minutes" time has passed. Expected Results: There should be a checkbox "Use Imap IDLE command" which causes mozilla mail to use it.
Sounds useful. I can't find any duplicates so I'm marking this NEW.
Status: UNCONFIRMED → NEW
Ever confirmed: true
Summary tweaking. Before: why not RFC2177 ? After: Support IMAP4 IDLE command (RFC 2177)
Summary: why not RFC2177 ? → Support IMAP4 IDLE command (RFC 2177)
Two things to consider here: Biff Support, for this there is an interesting comment in Bug 18266 (comment 154) - direct link and whether to open an additional TCP connection which we poll at least every 29 minutes according to the RFC or change nsImapProtocol to leave the TCP connection open, if this is not already done (I don't know the code well enough yet, my feeling is the connection is closed). The latter is the preferred solution.
we do cache connections (i.e., keep them open). This would probably be a fun little project for a mozilla contributor interested in imap.
Keywords: helpwanted
It's on my todo list, but I want to properly fix the namespace issues first.
FYI: Courier-IMAP 1.6 adds significant functionality to its IMAP IDLE implementation. On server platforms that have SGI's File Alteration Monitor installed (Linux, Irix, with partial xBSD support) IDLE generates real-time folder status updates (when multiple client sessions have the same folder selected, all clients are notified immediately when any client makes any changes to the folder, and immediately upon arrival of new mail). I scavenged an old laptop with MS OE 4.0, and opened a folder, then also logged in using pine. Even though pine doesn't do IDLE, I played with it, marking messages as deleted and undeleted, expunging the folder, and copying messages into this folder. On the other monitor, OE 4.0 obediently repeated everything I was doing in pine. Worked rather well. So, the scoreboard right now has two of the top three non-commercial IMAP servers offering value-added IMAP IDLE functionality.
QA Contact: huang → gchan
Re: Comment #6, yes I upgraded my courier-imap server very recently and added in FAM support. Outlook Express works very well with this extension and I would love to see it in Mozilla Mail at some point! Also, just thought I'd point out that Exchange 5.5 Server (and 2000 Server, AFAIK) support this extension.
I would like to have this feature added also It seems that the person that this is assigned to is (gone) ??? and this has been sitting without any additional comments for quite a while.. It seems that Mozilla is one of the few Email clients that do not implement the IDLE functionality yet..
Whiteboard: parity-oe
Add my vote for this... :) Moral support.
Could somebody with adequate permissions change the assignee of this bug. It using Scott MacGregor's old e-mail address. He now uses mscott@mozilla.org. Thanks.
I think I'm more likely to do this at some point - I've looked into it a little. What we'd need to do is set a timer and occasionally poll the transport to see if data was available, when in Idle mode. If data was available, we'd have to parse it. Darin has pointed out that timers like this are death on laptop batteries, so we need a way to turn this off - I've suggested a laptop mode setting that various components that used timers could check...
Assignee: mscott → bienvenu
(In reply to comment #11) > What we'd need to do is set a timer and occasionally poll the transport to see > if data was available, when in Idle mode. Pardon my ignorance but I thought the purpose of IDLE mode is to open up a connection that let the IMAP server know the client could receive updates whenever they happen. I'm unfamiliar with the the inner workings of Mozilla's IMAP communications but is there a way to make this event driven so that the arrival of data after the IDLE command is sent would trigger the parsing activity?
the problem is that we use blocking reads in the imap code, i.e., we can only read data in blocking mode. (This is for performance reasons - it's literally twice as fast). But we can't just issue an OnIdle and then go into a blocking read, because we still need to be able to re-use the connection in case the user wants to do something like read a message in that folder...unless we can actually issue a command on a transport that's in a blocking read - I kinda doubt that, though. If we could change the transport into a non-blocking mode to do OnIdle, then we'd do that, but transports can't do that - as I understand it, there are race conditions when you switch, etc...
david: can we do this: after issuing an OnIdle, periodically have the IMAP thread check Available on the socket transport's nsIInputStream. if it returns non-zero, then begin a blocking read until all of the data has been consumed. if it returns zero, then put the IMAP thread to sleep until another timeout event occurs or until some other user initiated command is issued that requires the IMAP connection. currently, ImapThreadMainLoop waits on m_urlReadyToRunMonitor. we could signal that monitor if there is either an "url ready to run" or an OnIdle Available check to process. wouldn't that be do-able without much hassle?
Darin, yes, that's more or less what I had in mind. I was responding to - what Wayne was saying, I think, was that ideally, we'd respond to OnIdle data immediately, instead of when the next timeout fired. I'm not sure how frequently we'd wake up and poll the transport, but I was thinking every 10 or 15 seconds - if we did the old non-blocking reads, we'd handle the data on demand...
hmm.... you just gave me an interesting idea. it turns out that nsIAsyncInputStream::AsyncWait can be called on a _blocking_ input stream just as easily as it can be called on a non-blocking input stream. so, you could continue to open blocking input streams, but then instead of using a timeout, you could just call AsyncWait on the stream. it will notify you when there is something to read (or when the stream closes). from that notification you can do the blocking read. you do not even need an event queue to handle the AsyncWait notification... you will get called on the socket transport thread... from which point you can tickle that monitor that will cause a blocking read to happen. going this route uses poll instead of a timer and should be all around much better. now, hopefully i'm not overlooking something! ;-)
(In reply to comment #11) > parse it. Darin has pointed out that timers like this are death on laptop > batteries, so we need a way to turn this off - I've suggested a laptop mode > setting that various components that used timers could check... David: How do other mail clients with IDLE support handle laptops? (I ask since I don't recall seeing "laptop mode" in a mail client before, but I could be wrong.)
Darin, that sounds like it's worth a try - it also sounds like I don't need to resurrect all the async notification code, which would be nice. Alex, I don't know off the top of my head, but it rings a vague bell that some programs have a laptop mode. It might also be the case that there's some win32 api or some linux api that tells you when you're in battery preservation mode and that's what I'm thinking of...
this is going to be very tricky... when the imap main loop gets notified that it has to do something (will have to change the name of the url ready to run monitor), it will check if there's no url to run, and we're idle - if so, we must have been told there's data to read. So, we'll invoke the imap parser, and tell it to parse a single line. That will cause it to do a blocking read for a single line. Then, we'll need to check if there's more data to parse (either in the input stream or the input stream line buffer - the input stream line buffer consumes all data available in the input stream, so maybe just the input stream line buffer), and if there is more data, we'll need to invoke the parser again, until there's no more data.). Currently, the parser doesn't know how to read just one line for a single unsolicited response, and we need to avoid the situation where the parser ends up doing a blocking read when there's no more data to come, because we need to be able to end the IDLE command whenever the user wants to run a url with that connection. So we need to teach the parser how to read just one line, and to be very careful not to try to do a blocking read when there's no data ready...
There is blog post from one of Microsoft Entourage IMAP engineer: As soon as this bug is closed it'll be great to post an update on the Mozilla Mail/Thunderbird in his blog entry as it got linked from MozillaZine (the way I got here as well).
OS: Windows 2000 → All
Hardware: PC → All
More trickiness - we probably don't want to immediately go into IDLE mode when a url finishes running in the INBOX because we might have another url waiting to run on the inbox, and we don't want to go into IDLE mode if we're just going to get out of it immediately. So I need to figure out if we can tell that there's a url waiting for a connection. We probably want to do IDLE for all idle connections, not just the INBOX connection, but the INBOX connection is the most important one. We could probably use the return value of nsImapIncomingServer::LoadNextQueuedUrl to know if we should go into idle mode. Except that there are some operations that chain urls - we'd need to make sure that the chaining prevents IDLE'ing. I'd really like to avoid using a timer to go into idle mode but I may end up going that way.
Status: NEW → ASSIGNED
This is a work-in-progress patch. It doesn't quite work, so don't try it! But it's most of the way there. The big problem is that connections get stuck after a couple operations, which I have to figure out. I also need to figure out if we want a per-server pref to control the use of IDLE (at first, we definitely will, in case there are problems). Do we have a pref UI for using the IDLE command or just use it if the server has it? For keeping connections alive, do we let the user set up biff to do that, or do we do it automatically? I probably also need to only go idle after a certain amount of inactive time, but I can do that later...
this seems to work well for me. I put all connections in the idle state when done with them. I immediately go IDLE when done with a url, unless we're going to run another URL immediately. the Check for new mail interval is orthogonal - we still run normal biffs even if IDLE is supported. This way, users can set the biff interval to whatever will keep the server connected, for most servers, 29 minutes. I had to diddle with the parser a little bit so that it knows to just parse a single line of idle response at a time, but it seems to be working fine.
Attachment #141982 - Attachment is obsolete: true
Comment on attachment 142178 [details] [diff] [review] proposed fix I had several comments I told david over AIM: 1) I think we will want UI in our account manager to allow laptop users to turn this off. I was searching through google to see if Outlook has the ability to turn it off but have not come up with anything yet. 2) I wonder if we will want to put a cap on the number of connections that can go into the IDLE state? 3) We should file a spin off bug to track having the client re-issue the IDLE command before the server times out. 4) Down the road, we may want to consider hooking up the idle state to a timer so we don't actually go into that state until the user has been idle for a certain period of time. Then again, going into the idle state may be cheap and we won't care.
Attachment #142178 - Flags: superreview?(mscott) → superreview+
On comment 24, item 1 perhaps Outlook might do it differently depending on the current power state of the machine? Perhaps sniffing traffic on Outlook when changing the power state of the macine... comparing a plugged in laptop to a battery mode laptop with a new session might function differntly?
On comment 24: 1- I don't mean to rehash things, but how bad is the IDLE command going to be on a laptop battery? Usually when I'm on battery, I'm either offline (so IDLE is moot) or I'm wireless, since if I'm close enought to be near an ethernet jack, usually power isn't too far off. The IDLE support will actually reduce the amount of traffic I send, since I can back off on the check new messages timer. Less traffic would seem to mean less power used by the wireless NIC. 4- Are we checking the status of the mailbox before we go into IDLE? IDLE will only show us what changes have occurred since the IDLE command started. If a mail message comes in or is modified outside of Mozilla after the last check but before we go in to IDLE, it won't show up until the messages are checked, right? On the other hand, polling the server before every IDLE may be too painful, especially for large mailboxes. Having to wait until the next scheduled poll may be acceptable, especially if the connection spends all it's time while not executing commands in an IDLE state, since that would make the window for unnoticed changes be the length of time to run the command. This would certainly be no worse than current behavior.
On comment 26: 1. The IDLE mode does not generate any server activity unless there are changes to the folder's contents. If the IDLE mode is implemented properly -- by waiting until the file descriptor is readable, instead of polling it -- the IDLE mode will not require any additional CPU. 4. Not true. If there are pending changes to the folder's status, a proper server IDLE implementation will immediately push those changes to the client as soon as the client enters the IDLE mode. To do otherwise will break the entire IMAP protocol itself.
(In reply to comment #24) > 2) I wonder if we will want to put a cap on the number of > connections that can go into the IDLE state? You mean connections to the same server right? Wouldn't it be a problem to have more than a single connection to the same server to be in IDLE state? More than one and we would receive and act on the same notifications multiple times.
Brodie, the notifications are on a per-folder basis. Each connection is for a particular folder, and we never have more than one connection for a particular folder.
fix checked in. bug 236584 spun off for the idle keep-alive issue.
Status: ASSIGNED → RESOLVED
Closed: 17 years ago
Resolution: --- → FIXED
Hi Mozilla People, I've just been writing the code for the other end of this problem, in an IMAP server, and thought I'd pass on some comments. (At the moment, my server does asynchronous notification, but I can't find any clients to test it with!) I think that the IDLE extension is a bit of a red herring. Normal IMAP servers without any extensions can send "unilateral" data AT ANY TIME. (Whether "real" servers actual do or not I don't know, but to quote from the RFC: "A client MUST be prepared to accept any server response at all times.") The difficulty is that normally you (the client) don't know if you're going to get these unilateral updates for new messages and activity on other connections, so you have to poll by sending NOOPs. With the IDLE extension, you KNOW that the server will send you updates without having to poll for them. Good luck - I'm looking forward to seeing this in Thunderbird soon. --Phil.
Phil, this in the nightly/weekly thunderbird builds now, and will be in .6 when it comes out. You do have a point about being prepared to accept input at any time - we should be waiting for input with a quiescent connection, even if we're not in IDLE mode because the server doesn't support IDLE. For the most part, we'll get that input the next time we try to do something with the connection.
hmm, I would like to reopen this because for me it seems buggy: - the idle state does notify the server that changes to the SELECTED mailbox should be pushed to the client. - as you always cache a maximum of 5 connections to the IMAP server the limit for observed folders is 5? If so, this should be communicated somehow. I see no solution for this problem without establishing more connections to the IMAP-Server. If I understand something wrong here, please prove me wrong. But I use the IDLE feature and always have some folders which are not notified unless I use "Check for new messages every ...".
> hmm, I would like to reopen this because for me it seems buggy: this is as designed. If you want, you can go into your advanced imap server prefs and increase the number of connections we'll hold open, but it's not a nice thing to do to your server...The RFC for the IDLE command doesn't say that we should keep open a connection for every folder you open in the UI, which kinda sounds like what you want to happen. If I understand you correctly, I think your complaint really has to do with the IDLE command, and not Mozilla's implementation of it.
The mozilla implementation (or documentation) is not really obvious. mozilla claims that the IDLE command is supported. But for what? There is no information about which folders will be "idled". (INBOX seems to be always IDLED). One IDLE session can only serve one folder. One thing would be a configuration option for every folder (up to max. connections) if it should be served by an idling imap server. The others have to be polled then.
Every cached connection we have (up to the max, default 5) is left in the IDLE state, instead of just idle :-) (assuming the connection is in the selected state, which they almost always are). It generally works out that the last 5 folders you selected in the UI have the 5 cached connections, so the last 5 folders you selected are in the IDLE state - accounting for the fact that we use one of those cached connections for the INBOX.
OK, understood. But this is not what I've expected. One thing is left which could be discussed. If one of the last five selected folders is not marked as "Check for new messages" it doesn't make much sense to IDLE this folder. What do you mean?
that's true, we could simply not IDLE connection that aren't set to be checked for new messages, and just leave them in the selected state...I could be wrong, but I'm getting the impression that you don't want us to cache connections to folders that aren't set to be checked for new messages, so that all the cached connections can be busy doing IDLE, and that's not the way it works - we cache connections to folders because we think you might be using them in the UI again (so that frequently used folders tend to stay cached).
I'm not sure if I'm rehashing what has already been discussed, but one thing I see is the IDLE enhancement detected new mail in folders I have not marked "Check for new messages", but have made active once. Not good. For example, I use server side filters to deliver to 3 folders as so: Inbox |-List1 |-List2 |-Spam I have "Check for new messages" checked on List1 and List2, but not Spam - I only want to check it occasionaly. Yet, as soon as I check "Spam" once, IDLE enhancement acts on it until I re-start Mozilla. This should not be...
To comment #39: I have to admit that your argument is correct. So let me shortly describe what was my initial problem: I've read that IDLE is supported now, so I deactivated the "Check for new mail every ... minutes". (hey, the mails will get pushed to me). After some days using this I observed that some does never notify me about new messages. hmm? Strange! Now I do understand that IDLE is only done in a best effort base and always for every folder which was opened some time before. It doesn't IDLE after startup but only if I accessed them before. That are some things which are confusing if you don't know it. And IMHO this is the word of RFC2177 but not the meaning. I want the IDLE state to get new mails pushed for folders which have the "Check for new mail" flag set. I understand that it's almost impossible to get the caching and the IDLING together. So comment #40 is true and not really wanted. All IMHO. And please note that I really like mozilla/thunderbird as IMAP client. I just want to give constructive feedback.
To fill in the "What would OE do?" question (and what I think is a sensible compromise), OE has one IDLE connection polling the INBOX at all times, and one IDLE connection polling the currently displayed folder. Other folders are updated only when viewed, or when the "Check for New Mail" runs every x minutes.
It does seem like Mozilla should make sure INBOX never gets dropped from the IDLE list...
Obviously, the only sensible response to comment #42 is, "OE sucks".
David, I suppose having IDLE scroll up the list window when (a) you're on the last line of the list and (b) new mail is received would be out of scope here?
yeah - out of scopoe - Idle acts just like get new mail, or biff, in that respect, so it's not particularly an IDLE issue. Re a previous comment, since we cache a connection to the INBOX, we will have an IDLE connection to the INBOX.
Product: MailNews → Core
Product: Core → MailNews Core | https://bugzilla.mozilla.org/show_bug.cgi?id=141369 | CC-MAIN-2020-24 | refinedweb | 4,051 | 69.31 |
You can subscribe to this list here.
Showing
1
results of 1
'sgoericke' writes:
> Because i'm a "beginner" in elisp maybe somebody could point me in the
> direction how to extend the eassist package to support nested namespaces? I use
> the ECB package too and it's method-buffer show all members even in nested
> namespaces so i think it's not a semantic problem.
Semantic indeed does support nested namespaces just fine. Do
M-x bovinate
to see the parser output Semantic returns. In the case of nested
namespaces, you get something like
(("foo" type
(("baz" type
(("bar" type
(:type "class")
(reparse-symbol namespacesubparts)
#<overlay from 54 to 107 in foo2.cpp>))
:type "namespace")
(reparse-symbol namespacesubparts)
#<overlay from 24 to 114 in foo2.cpp>))
:type "namespace")
nil #<overlay from 1 to 118 in foo2.cpp>))
(Just ignore the 'reparse symbol' and overlays; they're not important
for this task).
You see that namespaces are parsed as types by Semantic (with keyword
":type namespace"). All types belonging to a namespace are listed as
":members", which can again be namespaces. It seems eassist just doesn't
look deep enough.
-David | http://sourceforge.net/p/cedet/mailman/cedet-devel/?viewmonth=201208&viewday=12 | CC-MAIN-2016-07 | refinedweb | 191 | 73.27 |
Solving Water Pouring Problem using KotlinI wanted to explore how I can rewrite the solution described by Martin Odersky using Kotlin and I realized two things - one is that the immutable data structures that Kotlin offers are simply wrappers over Java Collections library and are not truly immutable, secondly the solution using Streams feature in Java will be difficult. However, the Vavr offers a good alternative to both - a first-class Immutable collections library and a Streams library and I took a crack at replicating the solution with Kotlin and Vavr.
A Cup looks like this, represented as a Kotlin data class:
import io.vavr.collection.List data class Cup(val level: Int, val capacity: Int) { override fun toString(): String { return "Cup($level/$capacity)" } }
Since the water pouring problem repesents the "state" of a set of cups, this can be simply represented as a "typealias" the following way:
typealias State = List<Cup>
There are 3 different types of moves that can be performed with the water in the cup - Empty it, Fill it, or Pour from one cup to another, represented again as Kotlin Data classes:
interface Move { fun change(state: State): State } data class Empty(val glass: Int) : Move { override fun change(state: State): State { val cup = state[glass] return state.update(glass, cup.copy(level = 0)) } override fun toString(): String { return "Empty($glass)" } } data class Fill(val glass: Int) : Move { override fun change(state: State): State { val cup = state[glass] return state.update(glass, cup.copy(level = cup.capacity)) } override fun toString(): String { return "Fill($glass)" } } data class Pour(val from: Int, val to: Int) : Move { override fun change(state: State): State { val cupFrom = state[from] val cupTo = state[to] val amount = min(cupFrom.level, cupTo.capacity - cupTo.level) return state .update(from, cupFrom.copy(cupFrom.level - amount)) .update(to, cupTo.copy(level = cupTo.level + amount)) } override fun toString(): String { return "Pour($from,$to)" } }
The implementation is making use of Vavr's List data structures "update" method to create a new list with just the relevant elements updated.
A "Path" represents a history of moves leading to the current state:
data class Path(val initialState: pour.State, val endState: State, val history: List<Move>) { fun extend(move: Move) = Path(initialState, move.change(endState), history.prepend(move)) override fun toString(): String { return history.reverse().mkString(" ") + " ---> " + endState } }
I am using the "prepend" method of the list to add elements to the beginning of history. Prepending to a list is an O(1) operation whereas appending is O(n), hence the choice.
Given a "state", a set of possible moves to change the "state" are the following -
1. Empty the glasses -
(0 until count).map { Empty(it) }
2. Fill the glasses -
(0 until count).map { Fill(it) }
3. Pour from one glass to another -
(0 until count).flatMap { from -> (0 until initialState.length()).filter { to -> from != to }.map { to -> Pour(from, to) } }
Now, all these moves are used for advancing from one state to another. Consider say 2 cups with capacity of 4 and 9 litres, initially filled with 0 litres of water, represented as "List(Cup(0/4), Cup(0/9))", with all possible moves the next set of states of the cups are the following:
Similarly, advancing each of these states to a new set of states would like this(in a somewhat simplified form):
As each State advances to a next set of states based on all possible moves, it can be seen that there will be an explosion of possible paths, this is where laziness offered by the Stream data structure of Vavr comes in. The values in a stream are only computed on request.
Given a set of paths, new paths are created using Stream the following way:
fun from(paths: Set<Path>, explored: Set<State>): Stream<Set<Path>> { if (paths.isEmpty) { return Stream.empty() } else { val more = paths.flatMap { path -> moves.map { move -> val next: Path = path.extend(move) next }.filter { !explored.contains(it.endState) } } return Stream.cons(paths) { from(more, explored.addAll(more.map { it.endState })) } } }
So, now given a stream of potential paths from the initial state to a new state, a solution to a "target" state becomes:
val pathSets = from(hashSet(initialPath), hashSet()) fun solution(target: State): Stream<Path> { return pathSets.flatMap { it }.filter { path -> path.endState == target } }
That covers the solution, a test with this code looks like this - there are two cups of 4 litre and 9 litre capacity, initially filled with 0 litres of water. The final target state is to get the second cup filled with 6 litres of water:
val initialState = list(Cup(0, 4), Cup(0, 9)) val pouring = Pouring(initialState) pouring.solution(list(Cup(0, 4), Cup(6, 9))) .take(1).forEach { path -> println(path) }
when run, this spits out the following solution:
Fill(1) Pour(1,0) Empty(0) Pour(1,0) Empty(0) Pour(1,0) Fill(1) Pour(1,0) Empty(0) ---> List(Cup(0/4), Cup(6/9))
Graphically represented, the solution looks like this:
It may be easier to simply follow a working version of the sample which is available in my github repo - | http://www.java-allandsundry.com/2019/03/ | CC-MAIN-2022-40 | refinedweb | 854 | 51.58 |
def words(word,number):
if number<len(word):
result={}
for key,value in word.items():
common_num=sorted(set(word.values()), reverse=True)[:number]
if value in common_num:
result.update({key:value})
word.clear()
word.update(result)
new_word_count={}
common_word=[]
common=[]
for key, value in word.items():
if value in common_word:
common.append(value)
common_word.append(value)
new_word_count=dict(word)
for key,value in new_word_count.items():
if value in common:
del word[key]
>>> word={'a': 2, 'b': 2, 'c' : 3, 'd: 3, 'e': 4, 'f' : 4, 'g' : 5}
>>> words(word,3)
Well, without any special imports, there are easier ways to accomplish what you're trying to do. You've got a whole lot of rigmarole involved in tracking and storing the values being kept, then deleting, then re-adding, when you could simplify a lot; even with explanatory comments, this is substantially shorter:
def common_words(word_count, number): # Early out when no filtering needed if number >= len(word_count): return # Get the top number+1 keys based on their values top = sorted(word_count, key=word_count.get, reverse=True)[:number+1] # We kept one more than we needed to figure out what the tie would be tievalue = word_count[top.pop()] # If there is a tie, we keep popping until the tied values are gone while top and tievalue == word_count[top[-1]]: top.pop() # top is now the keys we should retain, easy to compute keys to delete todelete = word_count.keys() - top for key in todelete: del word_count[key]
There are slightly better ways to do this that avoid repeated lookups in
word_count (sorting
items, not
keys, etc.), but this is easier to understand IMO, and the extra lookups in
word_count are bounded and linear, so it's not a big deal. | https://codedump.io/share/Y5eAWLu1VBzO/1/word-count-in-python | CC-MAIN-2017-09 | refinedweb | 287 | 51.48 |
Created on 2018-09-27 07:14 by lfriedri, last changed 2021-04-04 02:29 by ateeq.
The following creates an OSError:
import ctypes
hasattr(ctypes.windll, 'test')
The expected behavior would be to return "False"
ctypes.windll is an instance of ctypes.LibraryLoader, which has a __getattr__ method that calls ctypes.WinDLL(name) and caches the result as an instance attribute. I suppose with chained exceptions it's reasonable to handle OSError in __getattr__ by raising AttributeError. For example:
class A:
def __init__(self, name):
raise OSError
class B:
def __getattr__(self, name):
try:
A(name)
except OSError:
raise AttributeError
Demo:
>>> b = B()
>>> b.test
Traceback (most recent call last):
File "<stdin>", line 4, in __getattr__
File "<stdin>", line 3, in __init__
OSError
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "<stdin>", line 1, in <module>
File "<stdin>", line 6, in __getattr__
AttributeError
>>> hasattr(b, 'test')
False
FYI, I recommend avoiding the cdll and windll LibraryLoader instances. I wish they were deprecated because globally caching CDLL and WinDLL instances leads to conflicts between projects that use the same shared libraries.
Thank you for your reply.
I am not sure if I understood correctly:
Do you suggest to modify ctypes.__init__.py so that the __getattr__ method of LibraryLoader catches the OSError and raises an AttributeError instead, as in your example?
> __getattr__ method of LibraryLoader catches the OSError and
> raises an AttributeError
Yes. It seems no one was keen to work on this. I think it's relatively easy, so I'll add that flag in case someone is looking for an easy issue.
First patch fixing only the issue at hand on master. LibraryLoader now catches OSError for FileNotFoundError and raises AttributeError. | https://bugs.python.org/issue34816 | CC-MAIN-2021-25 | refinedweb | 291 | 56.35 |
-stable astack pointer that doesn't match the rest of the segments. Make ourbest attempt at untangling the resulting mess.Signed-off-by: H. Peter Anvin <hpa@zytor.com>Signed-off-by: Greg Kroah-Hartman <gregkh@suse.de>--- arch/i386/boot/boot.h | 4 +-- arch/i386/boot/header.S | 62 ++++++++++++++++++++++++++++++++++-------------- 2 files changed, 46 insertions(+), 20 deletions(-)--- a/arch/i386/boot/boot.h+++ b/arch/i386/boot/boot.h@@ -17,6 +17,8 @@ #ifndef BOOT_BOOT_H #define BOOT_BOOT_H +#define STACK_SIZE 512 /* Minimum number of bytes for stack */+ #ifndef __ASSEMBLY__ #include <stdarg.h>@@ -198,8 +200,6 @@ static inline int isdigit(int ch) } /* Heap -- available for dynamic lists. */-#define STACK_SIZE 512 /* Minimum number of bytes for stack */- extern char _end[]; extern char *HEAP; extern char *heap_end;--- a/arch/i386/boot/header.S+++ b/arch/i386/boot/header.S@@ -173,7 +173,8 @@ ramdisk_size: .long 0 # its size in byt bootsect_kludge: .long 0 # obsolete -heap_end_ptr: .word _end+1024 # (Header version 0x0201 or later)+heap_end_ptr: .word _end+STACK_SIZE-512+ # (Header version 0x0201 or later) # space from here (exclusive) down to # end of setup code can be used by setup # for local heap purposes.@@ -225,28 +226,53 @@ start_of_setup: int $0x13 #endif -# We will have entered with %cs = %ds+0x20, normalize %cs so-# it is on par with the other segments.- pushw %ds- pushw $setup2- lretw--setup2: # Force %es = %ds movw %ds, %ax movw %ax, %es cld -# Stack paranoia: align the stack and make sure it is good-# for both 16- and 32-bit references. In particular, if we-# were meant to have been using the full 16-bit segment, the-# caller might have set %sp to zero, which breaks %esp-based-# references.- andw $~3, %sp # dword align (might as well...)- jnz 1f- movw $0xfffc, %sp # Make sure we're not zero-1: movzwl %sp, %esp # Clear upper half of %esp- sti+# Apparently some ancient versions of LILO invoked the kernel+# with %ss != %ds, which happened to work by accident for the+# old code. If the CAN_USE_HEAP flag is set in loadflags, or+# %ss != %ds, then adjust the stack pointer.++ # Smallest possible stack we can tolerate+ movw $(_end+STACK_SIZE), %cx++ movw heap_end_ptr, %dx+ addw $512, %dx+ jnc 1f+ xorw %dx, %dx # Wraparound - whole segment available+1: testb $CAN_USE_HEAP, loadflags+ jnz 2f++ # No CAN_USE_HEAP+ movw %ss, %dx+ cmpw %ax, %dx # %ds == %ss?+ movw %sp, %dx+ # If so, assume %sp is reasonably set, otherwise use+ # the smallest possible stack.+ jne 4f # -> Smallest possible stack...++ # Make sure the stack is at least minimum size. Take a value+ # of zero to mean "full segment."+2:+ andw $~3, %dx # dword align (might as well...)+ jnz 3f+ movw $0xfffc, %dx # Make sure we're not zero+3: cmpw %cx, %dx+ jnb 5f+4: movw %cx, %dx # Minimum value we can possibly use+5: movw %ax, %ss+ movzwl %dx, %esp # Clear upper half of %esp+ sti # Now we should have a working stack++# We will have entered with %cs = %ds+0x20, normalize %cs so+# it is on par with the other segments.+ pushw %ds+ pushw $6f+ lretw+6: # Check signature at end of setup cmpl $0x5a5aaa55, setup_sig-- -To unsubscribe from this list: send the line "unsubscribe linux-kernel" inthe body of a message to majordomo@vger.kernel.orgMore majordomo info at read the FAQ at | https://lkml.org/lkml/2007/11/15/44 | CC-MAIN-2017-09 | refinedweb | 543 | 73.07 |
Typically subnetting is done by a router or a VLAN capable switch.
A Windows Active Directory Environment can handle a large # of users spread over a large geographical area by the use of sites. Windows AD defines a site as a subnet connected by fast links. Creating sites and associating a subnet to a site is done in Active Directroy Sites and services. A DC or GC along with operational master roles do not need to be installed in a site if the site has a small number of users or a small # of users and not servers in the site. If you create your site in AD sites and services and associate that site to a subnet, users on that subnet can access the Global Catalog at another site for log in. All that is needed is a WAN link [typically complished by a router].
Note: you can have 1 large site in a single domain. you can have multiple sites in a single domain and you can have multiple domains within a site [but you need multiple DCs to service the multiple domains within a site] remember a site is a subnet connected by fast links and is not a logical structure [like AD and Domains are] but a physical structure.
What confuses a lot of people is the logical structure of Active Directory and Domains vs the physical structure [topolopy] of a network. Sites are physical structures because they are subnets connected by fast links. your second subnet can be setup as a site [if you want and if your practicing setting up sites on a test network] and using the best practice of small # of users or small number of users and no servers in a site [provided the site has reliable and fast link] you don't need a DC or GC at the site.
I put in a suggestion here and for some reason it doesn't show up. I'll try to recap.
First to answer your question do you absolutely need to have another set of domain servers? No you don't.
If you continue to user your existing W2K DNS servers, how does the new subnet login to the domain? By creating a Site in AD sites and Services, then associating that site with the subnet.
Sites are subnets connected via Fast links. A router is normally used for subnetting but you can use a VLAN as well. Sites do not have to be in different physical locations [as in a test network setup where the subnets are seperated by a router and the 2 routers that connect the subnets together happen to be within 3 ft of each other] but a site is typically thought of as a in a different physical location than other sites. Best practice is that is sites have a small # of users and a fast reliable link that has adequate bandwidth and/or small # of users and no server, then you don't need a GC at the site for user login. They can use the fast reliable WAN link that has adequate bandwidth to use a GC at another site for log in.
Hope that helps ya.
Text book stuff.
Note: users who VPN in through RRAS are remote users and when they make a connection its as if they are directly connected to the network which is NOT the same as a site defined in Active Directory. AD sites are well connected subnets basically using dedicated lines router to router.
I have looked into setting up sites in AD. I manage to setup another site. But without a server assigned to that site, how would login from the other subnet be able to resolve? How would the other subnet be able to find the DHCP server? Therefore, I would really need at least a DHCP server (maybe from router) to assign the IPs before they can find where is the gateway?
welp, it goes like this, clients are configured to look for remote DNS servers over the WAN link in which to authenticate to not local DNS servers on their subnet [which there isn't any] [DNS provides the SVR and PTR records to the DC Global Catalog server]. This is done on a dedicated link NOT via the internet. If you want and are running DHCP on one subnet and want that DHCP server to issue IP addresses to computers on another subnet, add in a DHCP relay agent on the subnet you need IP addresses for. You can create different scopes of IP address in DHCP for different DNS zones in the DNS namespace. Therefore you can create a site, associate a subnet to that site, then give that site it's own DNS namespace [zone], create a scope of IP addresses in DHCP and for that zone, authorize DHCP for the zone to service clients in that site [it's own DNS namespace].
Network redesigning problem....
All clients connect to domain with this credentials assigned by DHCP server from both the windows2000 server.
ip : 192.168.1.x
subnet : 255.255.255.0
dns 1 : 192.168.1.2
dns 2 : 192.168.1.3
gateway : 192.168.1.4 (linux server)
So for, no problem. But now, I want to add another subnet to the system. Perhaps 192.168.2.x. But I am not sure how to do this.
I was thinking of adding another NIC to the linux server and it will act as a router to connect the 2 subnet. But then, what about the win2k servers and the DNS servers? If I continue using the win2k servers like this, how does the new subnet login to the domain? Do I absolutely need to have another set of domain servers?
This conversation is currently closed to new comments. | https://www.techrepublic.com/forums/discussions/network-redesigning-problem/ | CC-MAIN-2018-13 | refinedweb | 972 | 69.62 |
While reviewing some code earlier his week, I came across a C# function which when reduced to its core essentials boiled down to the following sample:
public void SomeMethod() { MessageBox.Show("hello world"); }
Off the top of your head do you think a C# compiler would happily accept this source code, or would you expect a syntax error?
The answer is that the above example function is completely valid C# source code. It is easier to see why once syntax highlighting has been applied to it.
The // characters after the http: prefix cause the rest of the URL to be interpreted as a comment, and the bit which is left (http:) is in the correct syntax to be interpreted as a label for use with the goto statement.
I had accidentally pasted a URL into my source code and checked it into our source control system. I didn’t notice for a few weeks since the code compiled and executed perfectly…
An amusing (but somewhat useless) application of this fact can be found in the following program
using System; public class MyDumbApplication { public static void Main() { Console.WriteLine("Hello World!"); goto http; } }
I wonder if this fact could be used to advantage in a International Obfuscated C Code Contest style C# program? | http://www.christec.co.nz/blog/archives/category/random-notes | CC-MAIN-2018-47 | refinedweb | 212 | 53.65 |
Getting ready for an IPv6-enabled Internet of Things
Well, it’s finally happened. We’ve exhausted the IPv4 address space. There are no more /8 IP addresses to be given out and the regional internet registries (RIRs) are scrounging for unused address space to reclaim. So what does this mean for the embedded developer? That’s what we’ll talk about in this paper.
The Internet Engineering Task Force (IETF) foresaw over a decade ago that we would eventually run out of IPv4 addresses to allocate. There were several estimates over the years as to exactly when the regional internet registries (RIRs) would run out of address blocks. Fortunately, the use of such things as network address translation (NAT), the dynamic host configuration protocol (DHCP) and classless inter-domain routing (CIDR) managed to hold off the inevitable for almost 6 years beyond the original estimates. However, the exhaustion of the IPv4 address space was as unavoidable as death and taxes. The so-called “X- day” occurred in mid April of 2011 as shown in Figure 1 .
But, what does “running out of addresses” actually mean to the Internet at large? Essentially, it means that any new requests for large blocks of address space cannot be met. No more ISPs with blocks of address space can be created. Now, IPv4 address space becomes a commodity that can be bargained, traded and potentially sold. And yet, the Internet continued to work.
In fact, in spite of exhausting the address space, nothing of any significance has happened… yet. As long as the major carriers keep their users at bay, the internet will continue to work just fine. However, there is a major block of addresses that, although allocated, hasn’t started to show up much – namely Africa. As more users from that block start to come online, the congestion in the core routers will continue to grow.
As more streaming services like Netflix, Hulu, iTunes and YouTube continue to gain popularity, the latency of traversing the so-called “middle boxes” like firewalls, NAT devices and the like will also continue to grow. This will also be exacerbated by streaming TV services to smartphones and tablets that are now being offered to mobile subscribers. With the number of mobile, Internet-aware devices continuing to increase, and the bandwidth to those devices expanding with the introduction of the long-term evolution (LTE) 4G phone service, we will start to reach a tipping point within the next few years where IPv4 will become a set of handcuffs that will hold the world’s insatiable desire for data hostage. Likely within the next 5 years, we’ll start talking about the tyranny of IPv4 and why it’s holding back progress.
OK, so that’s something to be concerned about for the future of IPv4 in the global Internet, but what about your embedded devices on private network segments? Well, as long as NAT continues to work or the devices have no need to access the Internet, then they’ll continue to work just fine. So, unless your O/S vendor completely drops IPv4 support, not likely in the next decade or so, you’ll be able to continue running for the foreseeable future. There is no compelling reason to incorporate IPv6 into your existing designs in these cases other than the desire to be “current” or if your customer requires it.
Here may lay the key feature that forces the issue. The U.S. Government has mandated the use of IPv6 by the end of 2012 and all federal agencies have had to demonstrate IPv6 capability and publish a statement that shows their compliance. In addition, the major carriers, largely prompted because the federal government is one of their largest customers, are also requiring that any device attached to their networks also be IPv6 capable. So again, existing sensor networks and embedded devices used by the federal government are “grandfathered”, but new devices will need to show IPv6 compliance. This means that we have the luxury of a transition period that may be on the order of a few years.
What if I'm a Middle-box Vendor?
On the other hand, if you’re a vendor of the middleware hardware and software boxes, then your future is lays on a somewhat different path. As stated previously, the federal government is mandating IPv6 support in all new equipment. Additionally, the major carriers are mandating it as well. This means that if you want to continue to sell your devices, you’ll have to bite the IPv6 bullet sooner or later.
For a large number of O/S platforms, this transition to IPv6 support is a fait acompli. Linux, Android, Windows, OS/X, and the xBSD platforms already support IPv6. In most, the support simply needs to be enabled. This can take the form of loading a driver or it may already be built in.
Once enabled, the network interfaces will show two separate addresses. One set for IPv4 and one for IPv6. These operating systems will also have a preference value that can be set to prefer using one or the other addresses. An example of the address duality can be seen in Figure 2 .
Having both protocols active is referred to as having a “dual-stack” capability. The two protocol stacks run in parallel. If you have both stacks active and are only using IPv4 addresses, then the primary overhead is simply the memory used by the IPv6 stack. The matching done on the version field of the IP header will then direct packets to one stack or the other.
Yet, the desktop O/Ses are not the only ones to have IPv6 support. Many of the major RTOS vendors also have IPv6 support. For some, it’s built in like the desktop O/S variants. In other cases, it’s an extra-cost option. For example, Wind River’s VxWorks, Enea’s OSE, RIM’s QNX all have IPv6 support. For Express Logic’s ThreadX, the stack itself is an extra-cost option, but IPv6 is available. However, operating systems like Micrium’s µC/OS-III only support IPv4 at the time of this writing. If IPv6 support for your embedded device is in your future, make sure to pick an O/S that supports it.
There is another benefit for embedded devices by switching to IPv6. The IPv4 protocol is notoriously complex requiring a fair amount of processing power to handle simple routing chores (Figure 3 ). The size of the IPv4 header can vary from 20 to as many as 60 octets depending on the enabled options. This can require a substantial amount of processing power to handle layer-3 switching.
On the other hand, an IPv6 header is always a fixed 40 octets and is considerably simpler (Figure 4 ). Much of the complexity of IPv4 is pushed off to subsequent protocol headers that need not be interrogated by layer-3 switches. This allows for many more packets-per-second through the same hardware with IPv6 when compared to IPv4.
How difficult is it to port to IPv6?
Let’s say that you’re committed to supporting IPv6, but you’ve got a lot of legacy IPv4 code. How hard is it to port to IPv6? Fortunately, it’s not that difficult.
First, realize that most of your old favorite commands like ping, traceroute, etc. have IPv6 versions with a “6” in their names. Therefore, ping becomes ping6, traceroute becomes traceroute6 and so on. Additionally, tools like tshark, WireShark, tcpdump, etc. are already IPv6 aware.
As for the programming APIs, only minor tweaks are typically needed to the code. The address family for IPv6 is AF_INET6 and the sockaddr_in structure is replaced by sockaddr_in6. As you might guess, most of the required changes to the code are in the area of setting up the addresses. The following is an example of an IPv4 server program that was converted to IPv6:
#include
#include < sysƒsocket.h>
#include < netinetƒin.h>
#include < stdio.h>
#include
…
main(argc, argv) /* server side */
int argc;
char *argv[];
{
int f;
/* */
/* OLD code: struct sockaddr_in from; */
/* OLD code: struct sockaddr_in sin; */
/* */
/* Change structure to sockaddr_in6 from sockaddr_in. */
/* */
struct sockaddr_in6 from;
struct sockaddr_in6 sin;
struct servent *sp;
sp = getservbyname(“login”, “tcp”);
if (sp == NULL) {
fprintf(stderr,
“rlogind: tcpƒlogin: unknown servicen”);
exit(1);
}
…
#ifndef DEBUU
/* Disassociate server from controlling terminal. */
…
#endif
memset((char *)&sin, 0, sizeof(sin));
/* */
/* OLD code: Not applicable. */
/* */
/* If the len member was not in the original IPv4 code */
/* add it now and make sure it is sin6_len for IPv6. */
/* */
sin.sin6_len = sizeof(sin);
/* */
/* OLD code: sin.sin_port = sp->s_port; */
/* */
/* Make sure you are using sockaddr_in6 members. */
/* */
sin.sin6_port = sp->s_port; /* Restricted port */
/* */
/* OLD code: sin.sin_addr.s_addr = INADDR_ANY; */
/* */
/* Make the modifications for assigning in6addr_any to */
/* sin6_addr. */
/* */
sin.sin6_addr = in6addr_any;
…
/* */
/* OLD code: f = socket(AF_INET, SOCK_STREAM, 0); */ /* */
/* Use the correct address family for IPv6. */ /* */
f = socket(AF_INET6, SOCK_STREAM, 0);
…
if (bind(f, (struct sockaddr *)&sin, sizeof(sin)) < 0) {
…
}
…
listen(f, 5);
for (;;) {
int g, len = sizeof(from);
g = accept(f, (struct sockaddr *) &from, &len);
if (g < 0) {
if (errno != EINTR)
syslog(LOU_ERR, “rlogind: accept: %m”); continue;
}
if (fork() == 0) {
close(f);
doit(g, &from);
}
close(g);
}
exit(0);
}
With the exception of the occasional “6” and the difference in handling the addresses, this looks pretty much the same as the IPv4 version. But, this raises the question of those pesky 128-bit IPv6 addresses.
IPv6 Addresses
Up to this point, we really haven’t made muchof an issue of what the IPv6 addresses look like or how they’reassigned. Considering that IPv6 addresses are four times the size ofIPv4 addresses, there must be a significant difference in how they’rehandled. This assumption is spot on.
First, forget about keepingIPv6 addresses in your head. With the exception of localhost (::1) andthe IPv6 version of INADDR_ANY (::), you don’t have much of a chance toremember them. First, the address is broken up into blocks of fourhexadecimal digits separated by “:”s. Leading zeros can be omitted andsuccessive blocks of zeros can be abbreviated as “::” although only one“::” sequence is permitted per address.
As an example, the following addresses are all equivalent:
2008:0db8:0000:0000:0000:0000:1978:57ac
2008:0db8:0:0:0:0:1978:57ac
2008:0db8::1978:57ac
2008:db8::1978:57ac
And, if you’re wondering how you enter a web address using the IPv6 address:
http://[2008:0db8::1978:57ac]/
https://[2008:0db8::1978:57ac]:443/
Clearly,these addresses will not be used by the public at large. These cry outfor using the domain name service (DNS). To configure DNS to supportIPv6, the records are not “A” records, but rather “AAAA” records:
$ sudo dig aaaa ipv6.google.com
; <<>> DiG 9.7.1-P2 <<>> aaaa ipv6.google.com
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 56332
;; flags: qr rd ra; QUERY: 1, ANSWER: 2, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;ipv6.google.com. IN AAAA
;; ANSWER SECTION:
ipv6.google.com. 900 IN CNAMEipv6.l.google.com.
ipv6.l.google.com. 300 IN AAAA 2001:4860:8003::93
Withsuch a large address space, how do we go about assigning an IPv6address to our interfaces? As it turns out, there are a number ofapproaches. Some of them are automatic, some require user intervention.
Oneof the goals of IPv6 is to restore end-to-end transparency to network.Essentially, eliminate the need for NAT boxes and allow devices to talkto each other as peers. If this is a goal, then we need to be able touniquely assign an IPv6 address. Therefore, one of the techniques forassigning addresses is to use the “link local” form of the address. Inthis technique, the MAC address of the interface is split in half andused in different portions of the IPv6 address.
Assuming anEthernet MAC of 5c:26:0a:26:76:dc, the link-local IPv6 address would be:fe80::5e26:0aff:fe26:76dc/64. Huh? The 48-bit MAC address is encoded asthe lower-order 64-bits of the IPv6 address. Let’s take a closer lookat the IPv6 address to decode it.
The first two octets of theaddress are “FE80”. This denotes a link-local address, e.g., one encodedfrom the MAC of the interface. The 6 octets of the MAC are then splitinto two equal pieces with “FFFE” sandwiched between. Finally, bit 1 ofthe first octet is set and the address is complete. This then becomes amodified IEEE EUI-64 identifier.
The advantage of this addressingapproach is that the address can now be uniquely traced to a singlemachine assuming that there are no duplicate MAC addresses floatingaround out there. This traceability is either good or bad depending onyour perspective. On the plus side, it helps diagnose connectivityproblems. On the bad side, it gives “evil-doers” more information aboutyour machine, like the manufacturer, than you’d really care to give out.
Ifyou don’t care for this addressing approach, then there are severalothers. One simply requires you to contact your site’s main router andhave the router assign an address using the State-less Automatic AddressConfiguration (SLAAC) protocol. Very similar to IPv4’s DHCP, SLAAC justassigns you the next available address, but doesn’t keep track of theaddresses you device was assigned. This means that each time you getboot, you’ll end up with a different IPv6 address.
In addition,there is an option to generate a more randomized address as per RFC 4941″Privacy Extensions for Stateless Address Autoconfiguration in IPv6″.With this feature enabled, the IPv6 address will be randomized acrossboots making it very difficult to correlate network traffic to aparticular device.
If you’d like more consistency inyour IPv6 addresses, then you have the option of using the statefulDHCPv6 server or manually assigning the address. Realize that the top 64bits of the address are likely assigned by your ISP, so you have tokeep those consistent so the core routers can find your network carrier.The remaining 64-bits are yours to choose including the application offurther subnet masks as assigned by the addressing authority for yoursite.
Security and IPsec
Another aspect of IPv6 that’sfrequently used as justification for its deployment is the use of theIPsec encryption layer. IPv6 has IPsec specified as an integral portionof the protocol. And yet, IPsec is also supported in IPv4 although ithasn’t seen wide-spread deployment in IPv4 networks. The notableexception is Cisco’s use of IPsec for their VPN solution and theLinux-based OpenSWAN/FreeSWAN VPNs.
IPsec is a link-encryptiontechnique. That is, each transaction is uniquely keyed and provides fordata integrity (the message won’t decrypt properly if it has beentampered with), data origin authentication (a unique key is used thatcan’t be forged from another location) and anti-replay facilities(sequence numbers can’t be duplicated). In addition, we can encrypt justthe security header or the header and the data payload as separatesteps depending on the security level desired.
This sounds greatin theory. And, given the layering of the protocols, routers need not gobeyond the top-layer IPv6 header into the encryption headers. Thisreduces the processing requirements for the middle boxes.
Unfortunately,in practice, the encryption key management is a bit on the complex sideand does not traverse NAT devices. Additionally, the process ofencrypting the traffic can place a significant overhead on datatransmission unless the device has hardware-based encryption engines.Therefore, although all IPv6 implementations will have support forIPsec, in practice there isn’t a lot of IPsec traffic traversing theInternet currently.
Are You Ready for IPv6?
June 6th,2012 was “World IPv6 Launch Day” (Figure 5 ). On that day, many of themajor ISPs and websites like Google, Yahoo!, Facebook, Akamai and otherspermanently enabled their IPv6 sites. Since then, the number ofIPv6-enabled websites has increased by roughly 2500%.
VariousIPv6 readiness tests are available on the Internet including going to. This site will test your IPv6 connectivity andprovide a report as seen in Figure 6 .
Ifyou happen to be serviced by one of the network service providers thatdo not already support IPv6 natively, all is not lost. There are anumber of ways for IPv4/IPv6 coexistence. In particular, there areseveral IPv6 tunneling techniques such as 6to4, Teredo, 6in4 and otherswith tunnel brokers that provide an endpoint as apoint-to-point of IPv6 ingress/egress for testing purposes. An exampleof a Teredo tunnel is shown in Figure 7 .
Aquick visit to your favorite search engine will show several otherwebsites that provide information and testing techniques to verify yourdevice’s ability to handle the future of IPv6 networks.
Summary
Unfortunately,we’ve merely scratched the surface on the issues associated with IPv6.But, hopefully you now have a better idea of what IPv6 is all about. Theissue ahead of you is if/how you’ll support IPv6 in your embeddedprojects?
Remember, if your devices are an isolated sensornetwork or similar application wherein all traffic is on the localnetwork, then you can likely ignore IPv6 for at least a few more years.However, if you are a mobile application or touch the Internet is someway, IPv6 is definitely in your future. As is the case for mostdevelopment, it’s a matter of time and money (and customer demand) as tohow soon you’ll be supporting IPv6.
If you get a few minutes,it’s likely in your best interest to go out to the various IPv6 testsites to see how your ISP and your equipment do in some of the simpletests. This will at least give you an idea of how much work lays aheadof you.
Michael Anderson is currently CTO and Chief Scientistfor The PTR Group, Inc. With over 35 years in the embedded and real-timecomputing industry, he works with a number of RTOS offerings. However,his focus over the past decade is primarily embedded Linux and Androidon a number of CPU architectures. This paper is based on content hepresented as part of a class at the Embedded SystemsConference on “Transitioning from IPv4 to IPv6 (ESC-423).” | https://www.embedded.com/getting-ready-for-an-ipv6-enabled-internet-of-things/ | CC-MAIN-2021-04 | refinedweb | 2,999 | 55.13 |
Hello -
I got confused about specifying colors and linewidths for LineCollections.
I think it would be helpful if the docstrings explicitly state that they should be sequences.
I know, they do in some way, but it i
Maybe we should even check this on input, as the error message you get when you don’t do that is confusing.
Let me explain:
from pylab import *
from matplotlib.collections import LineCollection
ax = subplot(111)
ax.add_collection( LineCollection( [[(0,0),(1,1)]], colors=‘r’ ) )
draw()
This works fine, as apparantly colors=‘r’ is interpreted as a sequence.
This does not work, however:
ax.add_collection( LineCollection( [[(0,0),(1,1)]], colors=‘r’, linewidths=2 ) )
draw()
Now I get an error: TypeError: CXX: type error. That’s not too helpful.
What does work is
ax.add_collection
( LineCollection( [[(0,0),(1,1)]], colors=‘r’, linewidths=[2] ) )
draw()
Maybe the confusing part is that just specifying colors=‘r’ works.
Thanks,
Mark
ps. I do all the draws as I am in interactive mode. | https://discourse.matplotlib.org/t/inconsistency-in-linecollection/8082 | CC-MAIN-2022-21 | refinedweb | 167 | 60.21 |
#include <cel_storage.h>
StorageRewinder class memorizes the storage pointer position on the construction and rewinds the storage pointer to the position on the destruction. This class is useful when a function/method should be rewind the storage pointer to the first position although it reads and seeks the storage in it. The following code illustrates how to use this class:
This constructor creates the StorageRewinder on the specified storage. The instance memorizes the current storage position of the storage.
This constructor creates the StorageRewinder that does not hold any storage. This version of constructor is usually used with setStorage method.
This method rewinds the storage to the initial position and delete the StorageRewinder instance.
This method releases the storage instance that is held by this instance. Please note that this method does not rewind the storage.
Referenced by setStorage().
This method rewinds the storage to the initial position.
Referenced by ~StorageRewinder().
This method associates the specified storage instance to this StorageRewinder instance. Please note that the previous one is not to be rewound but only released. | https://www.cuminas.jp/sdk/classCelartem_1_1StorageRewinder.html | CC-MAIN-2017-51 | refinedweb | 176 | 67.35 |
09 June 2011 16:33 [Source: ICIS news]
LONDON (ICIS)--Average daily chlorine production in the EU plus Norway and Switzerland fell by 7.3% in May from the previous month, while inventories of co-product caustic soda decreased by 8.3%, industry body Euro Chlor said on Thursday.
Average daily output of chlorine was 25,470 tonnes in May compared with 27,487 in April. On a year-on-year basis, May output was 9.5% lower.
The region produced 789,576 tonnes of chlorine in May compared with 824,602 tonnes in April.
Average capacity utilisation fell by 5.8 percentage points from April to 73% in May.
Caustic soda stocks reached 234,405 tonnes, an 8.3% decrease from April. This was the lowest level of inventories recorded in 2011. Year-on-year, stocks were 26,265 tonnes below May 2010.
?xml:namespace>
EU 27 + Norway/Switzerland Chlorine production & capacity utilisation
EU 27 + Norway/Switzerland
Chlorine production & capacity utilisation
Caustic soda stocks (tonnes)
For more on chlorine and caust | http://www.icis.com/Articles/2011/06/09/9468130/may-average-daily-chlorine-production-in-europe-falls-7.3.html | CC-MAIN-2015-11 | refinedweb | 172 | 68.16 |
The History of the Rise, Progress and Accomplishment of the Abolition of the African Slave Trade by the British Parliament (1808)
by
Thomas Clarkson
Part 4 out of 6
FullBooks.com homepage
Index of The History of the Rise, Progress and Accomplishment of the Abolition of the African Slave Trade by the British Parliament (1808)
Previous part (3)
Next part (5)
their great work, elected Sir William Dolben, baronet, Henry Thornton,
Lewis Alexander Grant, and Matthew Montagu, esquires, who were members of
parliament, and Truman Harford, Josiah Wedgwood, jun. esquire, and John
Clarkson, esquire, of the royal navy, as members of their own body; and
they elected the Reverend Archdeacon Plymloy (now Corbett) an honorary and
corresponding member, in consequence of the great services which he had
rendered their cause in the shires of Hereford and Salop, and the adjacent
counties of Wales.
The several committees, established in the country, on receiving the
resolutions and report as before mentioned, testified their sympathy in
letters of condolence to that of London on the late melancholy occasion;
and expressed their determination to support it as long as any vestiges of
this barbarous traffic should remain.
At length the session ended; and though, in the course of it, the
afflicting loss of the general question had occurred, there was yet an
attempt made by the abolitionists in parliament, which met with a better
fate. The Sierra Leone company received the sanction of the legislature.
The object of this institution was to colonize a small portion of the coast
of Africa. They, who were to settle there, were to have no concern in the
Slave-trade, but to discourage it as much as possible. They were to
endeavour to establish a new species of commerce, and to promote
cultivation in its neighbourhood by free labour. The persons more generally
fixed upon for colonists, were such Negros, with their wives and families,
as chose to abandon their habitations in Nova Scotia. These had followed
the British arms in America; and had been settled there, as a reward for
their services, by the British government.. He embarked more than eleven hundred
persons in fifteen vessels, of all which he took the command. On landing
them he became the first Governor of the new Colony. Having laid the
foundation of it, he returned to England; when a successor was appointed.
From that time many unexpected circumstances, but particularly devastations
by the French in the beginning of the war, took place, which, contributed
to ruin the trading company, which was attached to it. It is pleasing,
however, to reflect, that though the object of the institution, as far as
mercantile profit was concerned, thus failed, the other objects belonging
to it were promoted. Schools, places of worship, agriculture, and the
habits of civilized life, were established. Sierra Leone, therefore, now
presents itself as the medium of civilization for Africa. And, in this
latter point of view, it is worth all the treasure which has been lost in
supporting it: for the Slave-trade, which was the great obstacle to this
civilization, being now happily abolished, there is a metropolis,
consisting of some hundreds of persons, from which may issue the seeds of
reformation to this injured continent; and which, when sown, may be
expected to grow into fruit without interruption. New schools may be
transplanted from thence into the interior. Teachers, and travellers on
discovery, may be sent from thence in various directions; who may return to
it occasionally as to their homes. The natives too, able now to travel in
safety, may resort to it from various parts. They may see the improvements
which are going on from time to time. They may send their children to it
for education. And thus it may become the medium[A] of a great intercourse
between England and Africa, to the benefit of each other.
[Footnote A: To promote this desirable end an association took place last
year, called The African Institution, under the patronage of the Duke of
Gloucester, as president, and of the friends to the African cause,
particularly of such as were in parliament, and as belonged to the
committee for the abolition of the Slave-trade.]
CHAPTER IV.
_Continuation from July 1791 to July 1792--Author travels round the kingdom
again--Object of his journey--People begin to leave off the use of
sugar--to form committees--and to send petitions to Parliament--Motion made
in the House of Commons for the immediate abolition of the trade--Debates
upon it--Abolition resolved upon, but not to commence till 1796--Resolution
taken to the Lords--Latter determine upon hearing evidence--Evidence at
length introduced--Further hearing of it postponed to the next session._
The defeat which we had just sustained, was a matter of great triumph to
our opponents. When they considered the majority in the House of Commons in
their favour, they viewed the resolutions of the committee, which have been
detailed, as the last spiteful effort of a vanquished and dying animal, and
they supposed that they had consigned the question to eternal sleep. The
committee, however, were too deeply attached to the cause, vanquished as
they were, to desert it; and they knew also too well the barometer of
public feeling, and the occasion of its fluctuations, to despair. In the
year 1787 the members of the House of Commons, as well as the people, were
enthusiastic in behalf of the abolition of the trade. In the year 1788 the
fair enthusiasm of the former began to fade. In 1789 it died. In 1790
prejudice started up as a noxious weed in its place. In 1791 this prejudice
arrived at its growth. But to what were these changes owing?--To delay;
during which the mind, having been gradually led to the question as a
commercial, had been gradually taken from it as a moral object. But it was
possible to restore the mind to its proper place. Add to which, that the
nation had never deserted the cause during this whole period.
It is much to the honour of the English people, that they should have
continued to feel for the existence of an evil which was so far removed
from their sight. But at this moment their feelings began to be
insupportable. Many of them resolved, as soon as parliament had rejected
the bill, to abstain from the use of West Indian produce.. They inculcated abstinence from these articles as a moral duty;
they inculcated it as a peaceable and constitutional measure; and they laid
before the reader a truth, which was sufficiently obvious, that if each
would abstain, the people would have a complete remedy for this enormous
evil in their own power.
While these things were going on, it devolved upon me to arrange all the
evidence on the part of the abolition under proper heads, and to abridge it
into one volume. It was intended that a copy of this should be sent into
different towns of the kingdom, that all might know, if possible, the
horrors (as far as the evidence contained them) of this execrable trade;
and as it was possible that these copies might lie in the places where they
were sent, without a due attention to their contents, I resolved, with the
approbation of the committee, to take a journey, and for no other purpose
than personally to recommend that they might be read.
The books, having been printed, were dispatched before me. Of this tour I
shall give the reader no other account than that of the progress of the
remedy, which the people were then taking into their own hands. And first I
may observe, that there was no town, through which I passed, in which there
was not some one individual who had left off the use of sugar. In the
smaller towns there were from ten to fifty by estimation, and in the larger
from two to five hundred, who had made this sacrifice to virtue. These were
of all ranks and parties. Rich and poor, churchmen and dissenters, had
adopted the measure. Even grocers had left off trading in the article, in
some places. In gentlemen's families, where the master had set the example,
the servants had often voluntarily followed it; and even children, who were
capable of understanding the history of the sufferings of the Africans,
excluded, with the most virtuous resolution, the sweets, to which they had
been accustomed, from their lips. By the best computation I was able to
make from notes taken down in my journey, no fewer than three hundred
thousand persons had abandoned the use of sugar.
Having travelled over Wales, and two thirds of England, I found it would be
impossible to visit Scotland on the same errand. I had already, by moving
upwards and downwards in parallel lines, and by intersecting these in the
same manner, passed over six thousand miles. By the best calculation I
could make, I had yet two thousand to perform. By means of almost incessant
journeyings night and day, I had suffered much in my health. My strength
was failing daily. I wrote therefore to the committee on this subject; and
they communicated immediately with Dr. Dickson, who, on being applied to,
visited Scotland in my stead. He consulted first with the committee at
Edinburgh relative to the circulation of the Abridgement of the Evidence.
He then pursued his journey, and, in conjunction with the unwearied efforts
of Mr. Campbel Haliburton, rendered essential service to the cause for this
part of the kingdom.
On my return to London I found that the committee had taken into their own
body T.F. Forster, B.M. Forster, and James West, esquires, as members; and
that they had elected Hercules Ross, esquire, an honorary and corresponding
member, in consequence of the handsome manner in which he had come forward
as an evidence, and of the peculiar benefit which had resulted from his
testimony to the cause.
The effects of the two journeys by Dr. Dickson and myself were soon
visible. The people could not bear the facts, which had been disclosed to
them by the Abridgement of the Evidence. They were not satisfied, many of
them, with the mere abstinence from sugar; but began to form committees to
correspond with that of London. The first of these appeared at Newcastle
upon Tyne, so early as the month of October. It consisted of the Reverend
William Turner as chairman, and of Robert Ormston, William Batson, Henry
Taylor, Ralph Bainbridge, George Brown, Hadwen Bragg, David Sutton, Anthony
Clapham, George Richardson, and Edward Prowit. It received a valuable
addition afterwards by the admission of many others. The second was
established at Nottingham. The Reverend Jeremiah Bigsby became the
president, and the Rev. G. Walker and J. Smith, and Mess. Dennison, Evans,
Watson, Hart, Storer, Bott, Hawkesley, Pennington, Wright, Frith, Hall, and
Wakefield, the committee. The third was formed at Glasgow, under the
patronage of David Dale, Scott Moncrieff, Robert Graham, Professor Millar,
and others. Other committees started up in their turn. At length public
meetings began to take place, and after this petitions to be sent to
parliament; and these so generally, that there was not a day for three
months, Sundays excepted, in which five or six were not resolved upon in
some places or other in the kingdom.
Of the enthusiasm of the nation at this time none can form an opinion but
they who witnessed it. There never was perhaps a season when so much
virtuous feeling pervaded all ranks. Great pains were taken by interested
persons in many places to prevent public meetings. But no efforts could
avail. The current ran with such strength and rapidity, that it was
impossible to stem it. In the city of London a remarkable instance
occurred. The livery had been long waiting for the common council to begin
a petition. But the lord mayor and several of the aldermen stifled it. The
former, indignant at this conduct, insisted upon a common hall. A day was
appointed; and, though the notice given of it was short, the assemblage was
greater than had ever been remembered on any former occasion. Scarcely a
liveryman was absent, unless sick, or previously engaged. The petition,
when introduced, was opposed by those who had prevented it in the common
council. But their voices were drowned amidst groans and hissings. It was
shortly after carried; and it had not been signed more than half an hour,
before it was within the walls of the House of Commons. The reason of this
extraordinary dispatch was, that it had been kept back by intrigue so late,
that the very hour, in which it was delivered to the House, was that in
which Mr. Wilberforce was to make his new motion.
And as no petitions were ever more respectable than those presented on this
occasion, as far as they breathed the voice of the people, and as far as
they were founded on a knowledge of the object which they solicited, so
none were ever more numerous, as far as we have any record of such
transactions. Not fewer than three hundred and ten were presented from
England; one hundred and eighty-seven from Scotland; and twenty from Wales.
Two other petitions also for the abolition came from England, but they were
too late for delivery. On the other side of the question, one was presented
from the town of Reading for regulation, in opposition to that for
abolition from the same place. There were also four against abolition. The
first of these was from certain persons at Derby in opposition to the other
from that town. The second was from Stephen Fuller, esquire, as agent for
Jamaica. The third from J. Dawson, esquire, a slave-merchant at Liverpool.
And the fourth from the merchants, planters, mortgagees, annuitants, and
others concerned in the West Indian colonies. Taking in all these
statements, the account stood thus. For regulation there was one; against
all abolition there were four; and for the total abolition of the trade
five hundred and nineteen.
On the second of April Mr. Wilberforce moved the order of the day; which
having been agreed to, Sir William Dolben was put into the chair.
He then began by soliciting the candid attention of the West Indians to
what he was going to deliver to the House. However others might have
censured them indiscriminately, he had always himself made a distinction
between them and their system. It was the latter only, which he reprobated.
If aristocracy had been thought a worse form of government than monarchy,
because the people had many tyrants instead of one, how objectionable must
be that form of it, which existed in our colonies! Arbitrary power could be
bought there by any one, who could buy a slave. The fierceness of it was
doubtless restrained by an elevation of mind in many, as arising from a
consciousness of superior rank and consequence: but, alas! it was too often
exercised there by the base and vulgar. The more liberal too of the
planters were not resident upon their estates. Hence a promiscuous censure
of them would be unjust, though their system would undoubtedly be odious.
As for the cure of this monstrous evil, he had shown, last year, that
internal regulations would not produce it. These could have no effect,
while the evidence of slaves was inadmissible. What would be the situation
of the bulk of the people of this country, if only gentlemen of five
hundred a-year were admitted as evidences in our courts of law? Neither was
the cure of it in the emancipation of the slaves. He did not deny that he
wished them this latter blessing. But, alas, in their present degraded
state, they were unfit for it! Liberty was the child of reason and order.
It was indeed a plant of celestial growth, but the soil must be prepared
for its reception. He, who would see it flourish and bring forth its proper
fruit, must not think it sufficient to let it shoot in unrestrained
licentiousness. But if this inestimable blessing was ever to be imparted to
them, the cause must be removed, which obstructed its introduction. In
short, no effectual remedy could be found but in the abolition of the
Slave-trade.
He then took a copious view of the advantages, which would arise both to
the master and to the slave, if this traffic were done away; and having
recapitulated and answered the different objections to such a measure, he
went to that part of the subject, in which he described himself to be most
interested.
He had shown, he said, last year, that Africa was exposed to all the
horrors of war; and that most of these wars had their origin in the
Slave-trade. It was then said, in reply, that the natural barbarity of the
natives was alone sufficient to render their country a scene of carnage.
This was triumphantly instanced in the king of Dahomey. But his honourable
friend Lord Muncaster, then in the House, had proved in his interesting
publication, which had appeared since, called Historical Sketches of the
Slave-trade and of its Effects in Africa, addressed to the People of Great
Britain, that the very cruelties of this king, on which so much stress had
been laid, were committed by him in a war, which had been undertaken
expressly to punish an adjacent people for having stolen some of his
subjects and sold them for slaves.
He had shown also last year, that kings were induced to seize and sell
their subjects, and individuals each other, in consequence of the existence
of the Slave-trade.
He had shown also, that the administration of justice was perverted, so as
to become a fertile source of supply to this inhuman traffic; that every
crime was punished by slavery; that false accusations were made, to procure
convicts; and that even the judges had a profit on the convictions.
He had shown again, that many acts of violence were perpetrated by the
Europeans themselves. But he would now relate others, which had happened
since. The captain of an English vessel, lying in the river Cameroons, sent
his boat with three sailors and a slave to get water. A Black trader seized
the latter, and took him away. He alleged in his defence, that the captain
owed him goods to a greater amount than the value of the slave; and that he
would not pay him.
This being told on board, the captain, and a part of his crew, who were
compelled to blacken their naked bodies that they might appear like the
natives, went on shore at midnight, armed with muskets and cutlasses. They
fired on the trader's dwelling, and killed three of his children on the
spot. The trader, being badly wounded, died while they were dragging him to
the boat; and his wife, being wounded also, died in half an hour after she
was on board the ship. Resistance having been made to these violent
proceedings, some of the sailors were wounded, and one was killed. Some
weeks after this affray, a chieftain of the name of Quarmo went on board
the same vessel to borrow some cutlasses and muskets. He was going, he
said, into the country to make war; and the captain should have half of his
booty. So well understood were the practices of the trade, that his request
was granted. Quarmo, however, and his associates, finding things favourable
to their design, suddenly seized the captain, threw him overboard, hauled
him into their canoe, and dragged him to the shore; where another party of
the natives, lying in ambush, seized such of the crew as were absent from
the ship. But how did these savages behave, when they had these different
persons in their power? Did they not instantly retaliate by murdering them
all? No--they only obliged the captain to give an order on the vessel to
pay his debts. This fact came out only two months ago in a trial in the
court of common pleas--not in a trial for piracy and murder--but in the
trial of a civil suit, instituted by some of the poor sailors, to whom the
owners refused their wages, because the natives, on account of the
villanous conduct of their captain, had kept them from their vessel by
detaining them as prisoners on shore. This instance, he said, proved the
dreadful nature of the Slave-trade, its cruelty, its perfidy, and its
effect on the Africans as well as on the Europeans, who carried it on. The
cool manner, in which the transaction was conducted on both sides, showed
that these practices were not novel. It showed also the manner of doing
business in the trade. It must be remembered too, that these transactions
were carrying on at the very time when the inquiry concerning this trade
was going forward in Parliament, and whilst the witnesses of his opponents
were strenuously denying not only the actual, but the possible, existence
of any such depredations.
But another instance happened only in August last. Six British ships, the
Thomas, Captain Phillips; the Wasp, Captain Hutchinson; the Recovery,
Captain Kimber, of Bristol; and the Martha, Captain Houston; the Betsey,
Captain Doyle; and the Amachree, (he believed,) Captain Lee, of Liverpool;
were anchored off the town of Calabar. This place was the scene of a
dreadful massacre about twenty years before. The captains of these vessels,
thinking that the natives asked too much for their slaves, held a
consultation, how they should proceed; and agreed to fire upon the town
unless their own terms were complied with. On a certain evening they
notified their determination to the traders; and told them, that, if they
continued obstinate, they would put it into execution the next morning. In
this they kept their word. They brought sixty-six guns to bear upon the
town; and fired on it for three hours. Not a shot was returned. A canoe
then went off to offer terms of accommodation. The parties however not
agreeing, the firing recommenced; more damage was done; and the natives
were forced into submission. There were no certain accounts of their loss.
Report said that fifty were killed; but some were seen lying badly wounded,
and others in the agonies of death, by those who went afterwards on shore.
He would now say a few words relative to the Middle Passage, principally to
show, that regulation could not effect a cure of the evil there. Mr. Isaac
Wilson had stated in his evidence, that the ship, in which he sailed, only
three years ago, was of three hundred and seventy tons; and that she
carried six hundred and two slaves. Of these she lost one hundred and
fifty-five. There were three or four other vessels in company with her, and
which belonged to the same owners. One of these carried four hundred and
fifty, and buried two hundred; another carried four hundred and sixty-six,
and buried seventy-three; another five hundred and forty-six, and buried
one hundred and fifty-eight; and from the four together, after the landing
of their cargoes, two hundred and twenty died. He fell in with another
vessel, which had lost three hundred and sixty-two; but the number, which
had been bought, was not specified. Now if to these actual deaths, during
and immediately after the voyage, we were to add the subsequent loss in the
seasoning, and to consider that this would be greater than ordinary in
cargoes which were landed in such a sickly state, we should find a
mortality, which, if it were only general for a few months, would entirely
depopulate the globe.
But he would advert to what Mr. Wilson said, when examined, as a surgeon,
as to the causes of these losses, and particularly on board his own ship,
where he had the means of ascertaining them. The substance of his reply was
this--That most of the slaves laboured under a fixed melancholy, which now
and then broke out into lamentations and plaintive songs, expressive of the
loss of their relations, friends, and country. So powerfully did this
sorrow operate, that many of them attempted in various ways to destroy
themselves, and three actually effected it. Others obstinately refused to
take sustenance; and when the whip and other violent means were used to
compel them to eat, they looked up in the face of the officer, who
unwillingly executed this painful task, and said with a smile, in their own
language, "Presently we shall be no more." This, their unhappy state of
mind, produced a general languor and debility, which were increased in many
instances by an unconquerable aversion to food, arising partly from
sickness, and partly, to use the language of the slave-captains, from
sulkiness. These causes naturally produced the flux. The contagion spread;
several were carried off daily; and the disorder, aided by so many powerful
auxiliaries, resisted the power of medicine. And it was worth while to
remark, that these grievous sufferings were not owing either to want of
care on the part of the owners, or to any negligence or harshness of the
captain; for Mr. Wilson declared, that his ship was as well fitted out, and
the crew and slaves as well treated, as any body could reasonably expect.
He would now go to another ship. That, in which Mr. Claxton sailed as a
surgeon, afforded a repetition of all the horrid circumstances which had
been described. Suicide was attempted, and effected; and the same barbarous
expedients were adopted to compel the slaves to continue an existence,
which they considered as too painful to be endured. The mortality also was
as great. And yet here again the captain was in no wise to blame. But this
vessel had sailed since the regulating act. Nay, even in the last year the
deaths on shipboard would be found to have been between ten and eleven per
cent. on the whole number exported. In truth, the House could not reach the
cause of this mortality by all their regulations. Until they could cure a
broken heart--until they could legislate for the affections, and bind by
their statutes the passions and feelings of the mind, their labour would be
in vain.
Such were the evils of the Passage. But evils were conspicuous every where,
in this trade. Never was there indeed a system so replete with wickedness
and cruelty. To whatever part of it we turned our eyes, whether to Africa,
the Middle Passage, or the West Indies, we could find no comfort, no
satisfaction, no relief. It was the gracious ordinance of Providence, both
in the natural and moral world, that good should often arise out of evil.
Hurricanes cleared the air; and the propagation of truth was promoted by
persecution. Pride, vanity, and profusion contributed often, in their
remoter consequences, to the happiness of mankind. In common, what was in
itself evil and vicious was permitted to carry along with it some
circumstances of palliation. The Arab was hospitable; the robber brave. We
did not necessarily find cruelty associated with fraud, or meanness with
injustice. But here the case was far otherwise. It was the prerogative of
this detested traffic to separate from evil its concomitant good, and to
reconcile discordant mischiefs. It robbed war of its generosity; it
deprived peace of its security: we saw in it the vices of polished society,
without its knowledge or its comforts; and the evils of barbarism without
its simplicity. No age, no sex, no rank, no condition was exempt from the
fatal influence of this wide-wasting calamity. Thus it attained to the
fullest measure of pure, unmixed, unsophisticated wickedness; and, scorning
all competition and comparison, it stood without a rival in the secure,
undisputed, possession of its detestable preeminence.
But, after all this, wonderful to relate, this execrable traffic had been
defended on the ground of benevolence! It had been said, that the slaves
were captives and convicts, who, if we were not to carry them away, would
be sacrificed, and many of them at the funerals of people of rank,
according to the savage custom of Africa. He had shown, however, that our
supplies of slaves were obtained from other quarters than these. But he
would wave this consideration for the present. Had it not been acknowledged
by his opponents, that the custom of ransoming slaves prevailed in Africa?
With respect to human sacrifices, he did not deny, that there might have
been some instances of these; but they had not been proved to be more
frequent than amongst other barbarous nations; and, where they existed,
being acts of religion, they would not be dispensed with for the sake of
commercial gain. In fact, they had nothing to do with the Slave-trade; only
perhaps, if it were abolished, they might, by means of the civilization
which would follow, be done away.
But, exclusively of these sacrifices, it had been asserted, that it was
kindness to the inhabitants to take them away from their own country. But
what said the historians of Africa, long before the question of the
abolition was started? "Axim," says Bosman, "is cultivated, and abounds
with numerous large and beautiful villages: its inhabitants are
industriously employed in trade, fishing, or agriculture."--"The
inhabitants of Adom always expose large quantities of corn to sale, besides
what they want for their own use."--"The people of Acron husband their
grounds and time so well, that every year produces a plentiful harvest."
Speaking of the Fetu country, he says, "Frequently, when walking through
it, I have seen it abound with fine well built and populous towns,
agreeably enriched with vast quantities of corn and cattle, palm-wine and
oil. The inhabitants all apply themselves without distinction to
agriculture; some sow corn; others press oil, and draw wine from the
palm-trees."
Smith, who was sent out by the royal African company in 1726, assures us,
"that the discerning natives account it their greatest unhappiness, that
they were ever visited by the Europeans. They say that we Christians
introduced the traffic of slaves; and that before our coming they lived in
peace. But, say they, it is observable, wherever Christianity comes, there
come swords and guns and powder and ball with it."
"The Europeans," says Bruce, "are far from desiring to act as peace-makers
among them. It would be too contrary to their interests; for the only
object of their wars is to carry off slaves; and, as these form the
principal part of their traffic, they would be apprehensive of drying up
the source of it, were they to encourage the people to live well together."
"The neighbourhood of the Damel and Tin keep them perpetually at war, the
benefit of which accrues to the Company, who buy all the prisoners made on
either side; and the more there are to sell, the greater is their profit;
for the only end of their armaments is to make captives, to sell them to
the White traders."
Artus, of Dantzic, says that in his time, "those liable to pay fines were
banished till the fine was paid; when they returned to their houses and
possessions."
Bosman affirms "that formerly all crimes in Africa were compensated by fine
or restitution, and, where restitution was impracticable, by corporal
punishment."
Moore says, "Since this trade has been used, all punishments have been
changed into slavery. There being an advantage in such condemnation, they
strain the crimes very hard, in order to get the benefit of selling the
criminal. Not only murder, theft, and adultery, are punished by selling the
criminal for a slave, but every trifling crime is punished in the same
manner."
Loyer affirms that "the King of Sain, on the least pretence, sells his
subjects for European goods. He is so tyrannically severe, that he makes a
whole village responsible for the fault of one inhabitant; and on the least
offence sells them all for slaves."
Such, he said, were the testimonies, not of persons whom he had summoned;
not of friends of the abolition: but of men who were themselves, many of
them, engaged in the Slave-trade. Other testimonies might be added; but
these were sufficient to refute the assertions of his opponents, and to
show the kind services we had done to Africa by the introduction of this
trade.
He would just touch upon the argument, so often repeated, that other
nations would carry on the Slave-trade, if we abandoned it. But how did we
know this? Had not Denmark given a noble example to the contrary? She had
consented to abolish the trade in ten years; and had she not done this,
even though we, after an investigation for nearly five years, had ourselves
hung back? But what might not be expected, if we were to take up the cause
in earnest; if we were to proclaim to all nations the injustice of the
trade, and to solicit their concurrence in the abolition of it! He hoped
the representatives of the nation would not be less just than the people.
The latter had stepped forward, and expressed their sense more generally by
petitions, than in any instance in which they had ever before interfered.
To see this great cause thus triumphing over distinctions and prejudices
was a noble spectacle. Whatever might be said of our political divisions,
such a sight had taught us, that there were subjects still beyond the reach
of party; that there was a point of elevation, where we ascended above the
jarring of the discordant elements, which ruffled and agitated the vale
below. In our ordinary atmosphere clouds and vapours obscured the air, and
we were the sport of a thousand conflicting winds and adverse currents; but
here we moved in a higher region, where all was pure and clear, and free
from perturbation and discomposure.
"As some tall cliff, that lifts its awful form,
Swells from the vale, and midway leaves the storm;
Though round its breast the rolling clouds are spread,
Eternal sunshine settles on its head."
Here then, on this august eminence, he hoped we should build the Temple of
Benevolence; that we should lay its foundation deep in Truth and Justice;
and that we should inscribe upon its gates, "Peace and Goodwill to Men."
Here we should offer the first-fruits of our benevolence, and endeavour to
compensate, if possible, for the injuries we had brought upon our
fellow-men.
He would only now observe, that his conviction of the indispensable
necessity of immediately abolishing this trade remained as strong as ever.
Let those who talked of allowing three or four years to the continuance of
it, reflect on the disgraceful scenes which had passed last year. As for
himself, he would wash his hands of the blood which would be spilled in
this horrid interval. He could not, however, but believe, that the hour was
come, when we should put a final period to the existence of this cruel
traffic. Should he unhappily be mistaken, he would never desert the cause;
but to the last moment of his life he would exert his utmost powers in its
support. He would now move, "That it is the opinion of this committee, that
the trade carried on by British subjects for the purpose of obtaining
slaves on the coast of Africa, ought to be abolished."
Mr. Baillie was in hopes that the friends of the abolition would have been
contented with the innocent blood which had been already shed. The great
island of St. Domingo had been torn to pieces by insurrections. The most
dreadful barbarities had been perpetrated there. In the year 1789 the
imports into it exceeded five millions sterling. The exports from it in the
same year amounted to six millions; and the trade employed three hundred
thousand tons of shipping, and thirty thousand seamen. This fine island,
thus advantageously situated, had been lost in consequence of the agitation
of the question or the Slave-trade. Surely so much mischief ought to have
satisfied those who supported it; but they required the total destruction
of all the West Indian colonies, belonging to Great Britain, to complete
the ruin.
The honourable gentleman, who had just spoken, had dwelt, upon the
enormities of the Slave-trade. He was far from denying, that many acts of
inhumanity might accompany it; but as human nature was much the same every
where, it would be unreasonable to expect among African traders, or the
inhabitants of our islands, a degree of perfection in morals, which was not
to be found in Great Britain itself. Would any man estimate the character
of the English nation by what was to be read in the records of the Old
Bailey? He himself, however, had lived sixteen years in the West Indies,
and he could bear testimony to the general good usage of the slaves.
Before the agitation of this impolitic question the slaves were contented
with their situation. There was a mutual confidence between them and their
masters: and this continued to be the case till the new doctrines were
broached. But now depots of arms were necessary on every estate; and the
scene was totally reversed. Nor was their religious then inferior to their
civil state. When the English took possession of Grenada, where his
property lay, they found them baptized and instructed in the principles of
the Roman Catholic faith. The priests of that persuasion had indeed been
indefatigable in their vocation; so that imported Africans generally
obtained within twelve months a tolerable idea of their religious duties.
He had seen the slaves there go through the public mass in a manner, and
with a fervency, which would have done credit to more civilized societies.
But the case was now altered; for, except where the Moravians had been,
there was no trace in our islands of an attention to their religious
interests.
It had been said, that their punishments were severe. There might be
instances of cruelty; but these were not general. Many of them were
undoubtedly ill disposed; though not more, according to their number, on a
plantation, than in a regiment, or in a ship's crew. Had we never heard of
seamen being flogged from ship to ship, or of soldiers dying in the very
act of punishment? Had we not also heard, even in this country of boasted
liberty, of seamen being seized, and carried away, when returning from
distant voyages, after an absence of many years; and this without even
being allowed to see their wives and families? As to distressed objects, he
maintained, that there was more wretchedness and poverty in St. Giles's,
than in all the West Indian islands belonging to Great Britain.
He would now speak of the African and West Indian trades. The imports and
exports of these amounted to upwards of ten millions annually; and they
gave employment to three hundred thousand tons of shipping, and to about
twenty-five thousand seamen. These trades had been sanctioned by our
ancestors in parliament. The acts for this purpose might be classed under
three heads. First, they were such as declared the colonies and the trade
thereof advantageous to Great Britain, and therefore entitled to her
protection. Secondly, such as authorised, protected, and encouraged the
trade to Africa, as advantageous in itself, and necessary to the welfare
and existence of the sugar colonies: and, Thirdly, such as promoted and
secured loans of money to the proprietors of the said colonies, either from
British subjects or from foreigners. These acts[A], he apprehended, ought
to satisfy every person of the legality and usefulness of these trades.
They were enacted in reigns distinguished for the production of great and
enlightened characters. We heard then of no wild and destructive doctrines
like the present. These were reserved for this age of novelty and
innovation. But he must remind the House, that the inhabitants of our
islands had as good a right to the protection of their property, as the
inhabitants of Great Britain. Nor could it be diminished in any shape
without full compensation. The proprietors of lands in the ceded islands,
which were purchased of government under specific conditions of settlement,
ought to be indemnified. They also (of whom he was one) who had purchased
the territory granted by the crown to General Monkton in the Island of St.
Vincent, ought to be indemnified also. The sale of this had gone on
briskly, till it was known, that a plan was in agitation for the abolition
of the Slave-trade. Since that period the original purchasers had done
little or nothing, and they had many hundred acres on hand, which would be
of no value, if the present question was carried. In fact, they had a right
to compensation. The planters generally spent their estates in this
country. They generally educated their children in it. They had never been
found seditious or rebellious; and they demanded of the Parliament of Great
Britain that protection, which, upon the principles of good faith, it was
in duty bound to afford them in common with the rest of his majesty's loyal
subjects.
[Footnote A: Here he quoted them specifically.]
Mr. Vaughan stated that, being a West Indian by birth and connected with
the islands, he could speak from his own knowledge. In the early part of
his life he was strongly in favour of the abolition of the Slave-trade. He
had been educated by Dr. Priestley and the father of Mrs. Barbauld; who
were both of them friends to that question. Their sentiments he had
imbibed: but, although bred at the feet of Gamaliel, he resolved to judge
for himself, and he left England for Jamaica.
He found the situation of the slaves much better than he had imagined.
Setting aside liberty, they were as well off as the poor in Europe. They
had little want of clothes or fuel: they had a house and garden found them;
were never imprisoned for debts; nor deterred from marrying through fear of
being unable to support a family; their orphans and widows were taken care
of, as they themselves were when old and disabled; they had medical
attendance without expense; they had private property, which no master ever
took front them; and they were resigned to their situation, and looked for
nothing beyond it. Perhaps persons might have been prejudiced by living in
the towns, to which slaves were often sent for punishment; and where there
were many small proprietors; or by seeing no Negro otherwise than as
belonging to the labouring poor; but they appeared to him to want nothing
but liberty; and it was only occasionally that they were abused.
There were two prejudices with respect to the colonies, which he would
notice. The first was, that cruel usage occasioned the inequality of births
and deaths among the slaves. But did cruelty cause the excess of deaths
above births in the city of London? No--this excess had other causes. So it
had among the slaves. Of these more males were imported than females: they
were dissolute too in their morals; they had also diseases peculiar to
themselves. But in those islands where they nearly kept up their numbers,
there was this difficulty, that the equality was preserved by the increase
on one estate compensating for the decrease on another. These estates,
however, would not interchange their numbers; whereas, where freedom
prevailed, the free labourers circulated from one employer to another, and
appeared wherever they were wanted.
The second was, that all chastisement of the slaves was cruelty. But this
was not true. Their owners generally withdrew them from public justice; so
that they, who would have been publicly executed elsewhere, were often kept
alive by their masters, and were found punished again and again for
repeating their faults. Distributive justice occasioned many punishments;
as one slave was to be protected against every other slave: and, when one
pilfered from another, then the master interfered. These punishments were
to be distinguished from such as arose from enforcing labour, or from the
cruelty of their owners. Indeed he had gone over the islands, and he had
seen but little ill usage. He had seen none on the estate where he resided.
The whip, the stocks, and confinement, were all the modes of punishment he
had observed in other places. Some slaves belonging to his father were
peculiarly well off. They saved money, and spent it in their own way.
But, notwithstanding all he had said, he allowed that there was room for
improvement; and particularly for instilling into the slaves the principles
of religion. Where this should be realized, there would be less punishment,
more work, more marriages, more issue, and more attachment to masters.
Other improvements would be the establishment of medical societies; the
introduction of task-work; and grants of premiums and honorary distinctions
both to fathers and mothers, according to the number of children which they
should rear. Besides this, Negro evidence should be allowed in the courts
of law, it being left to the discretion of the court or jury to take or
reject it, according to the nature of the case. Cruel masters also should
be kept in order in various ways. They should be liable to have their
slaves taken from them, and put in trust. Every instrument of punishment
should be banished, except the whip. The number of lashes should be
limited; and the punishment should not be repeated till after intervals.
These and other improvements should be immediately adopted by the planters.
The character of the exemplary among them was hurt by being confounded with
that of lower and baser men. He concluded by stating, that the owners of
slaves were entitled to compensation, if, by means of the abolition, they
should not be able to find labourers for the cultivation of their lands[A].
[Footnote A: Mr. Vaughan declared in a future stage of the debate, that he
wished to see a prudent termination both of the Slave-trade and of slavery;
and that, though he was the eldest son of his father, he never would, on
any consideration, become the owner of a slave.]
Mr. Henry Thornton conceived, that the two last speakers had not spoken to
the point. The first had described the happy state of the slaves in the
West Indies. The latter had made similar representations; but yet had
allowed, that much improvement might be made in their condition. But this
had nothing to do with the question then before them. The manner of
procuring slaves in Africa was the great evil to be remedied. Africa was to
be stripped of its inhabitants to supply a population for the West Indies.
There was a Dutch proverb, which said, "My son, get money, honestly if you
can--but get money:" or, in other words, "Get slaves, honestly if you
can--but get slaves." This was the real grievance; and the two honourable
gentlemen, by confining their observations to the West Indies, had entirely
overlooked it.
Though this evil had been fully proved, he could not avoid stating to the
House some new facts, which had come to his knowledge as a director of the
Sierra Leone Company, and which would still further establish it. The
consideration, that they had taken place since the discussion of the last
year on this subject, obliged him to relate them.
Mr. Falconbridge, agent to the Company, sitting one evening in Sierra
Leone, heard a shout, and immediately afterwards the report of a gun.
Fearing an attack, he armed forty of the settlers, and rushed with them to
the place from whence the noise came. He found a poor wretch, who had been
crossing from a neighbouring village, in the possession of a party of
kidnappers, who were tying his hands. Mr. Falconbridge, however, dared not
rescue him, lest, in the defenceless state of his own town, retaliation
might be made upon him.
At another time a young woman, living half a mile off, was sold, without
any criminal charge, to one of the slave-ships. She was well acquainted
with the agent's wife, and had been with her only the day before. Her cries
were heard; but it was impossible to relieve her.
At another time a young lad, one of the free settlers who went from
England, was caught by a neighbouring chief, as he was straggling alone
from home, and sold for a slave. The pretext was, that some one in the town
of Sierra Leone had committed an offence. Hence the first person belonging
to it, who could be seized, was to be punished. Happily the free settlers
saw him in his chains; and they recovered him, before he was conveyed to
the ship.
To mark still more forcibly the scenes of misery, to which the Slave-trade
gave birth, he would mention a case stated to him in a letter by King
Naimbanna. It had happened to this respectable person, in no less than
three instances, to have some branches of his family kidnapped, and carried
off to the West Indies. At one time three young men, Corpro, Banna, and
Marbrour, were decoyed on board a Danish slave-ship, under pretence of
buying something, and were taken away. At another time another relation
piloted a vessel down the river. He begged to be put on shore, when he came
opposite to his own town; but he was pressed to pilot her to the river's
mouth. The captain then pleaded the impracticability of putting him on
shore; carried him to Jamaica; and sold him for a slave. Fortunately,
however, by means of a letter, which was conveyed there, the man, by the
assistance of the governor, was sent back to Sierra Leone. At another time
another relation was also kidnapped. But he had not the good fortune, like
the former, to return.
He would mention one other instance. A son had sold his own father, for
whom he obtained a considerable price: for, as the father was rich in
domestic slaves, it was not doubted that he would offer largely for his
ransom. The old man accordingly gave twenty-two of these in exchange for
himself. The rest, however, being from that time filled with apprehensions
of being on some ground or other sold to the slave-ships, fled to the
mountains of Sierra Leone, where they now dragged on a miserable existence.
The son himself was sold, in his turn, soon after. In short, the whole of
that unhappy peninsula, as he learnt from eye-witnesses, had been desolated
by the trade in slaves. Towns were seen standing without inhabitants all
over the coast; in several of which the agent of the Company had been.
There was nothing but distrust among the inhabitants. Every one, if he
stirred from home, felt himself obliged to be armed.
Such was the nature of the Slave-trade. It had unfortunately obtained the
name of a trade; and many had been deceived by the appellation. But it was
war, and not trade. It was a mass of crimes, and not commerce. It was that
which prevented the introduction of a trade in Africa; for it was only by
clearing and cultivating the lands, that the climate could be made healthy
for settlements; but this wicked traffic, by dispersing the inhabitants,
and causing the lands to remain uncultivated, made the coast unhealthy to
Europeans. He had found, in attempting to establish a colony there, that it
was an obstacle, which opposed itself to him in innumerable ways; it
created more embarrassments than all the natural impediments of the
country; and it was more hard to contend with, than any difficulties of
climate, soil, or natural disposition of the people.
We would say a few words relative to the numerous petitions, which were
then on the table of the House. They had shown, in an extraordinary manner,
the opinion of the people. He did not wish to turn this into a
constitutional question; but he would observe, that it was of the utmost
consequence to the maintenance of the constitution of this country, that
the reputation of Parliament should be maintained. But nothing could
prejudice its character so much, as a vote, which should lead the people to
believe, that the legislative body was the more corrupt part of it, and
that it was slow to adopt moral principles.
It had been often insinuated that Parliament, by interfering in this trade,
departed from its proper functions. No idea could be more absurd: for, was
it not its duty to correct abuses? and what abuses were greater than
robbery and murder? He was indeed anxious for the abolition. He desired it,
as a commercial man, on account of the commercial character of the country.
He desired it for the reputation of Parliament, on which so materially
depended the preservation of our happy constitution: but most of all he
prayed for it for the sake of those eternal principles of justice, which it
was the duty of nations, as well as of individuals, to support.
Colonel Tarleton repeated his arguments of the last year. In addition to
these he inveighed bitterly against the abolitionists, as a junto of
sectaries, sophists, enthusiasts, and fanatics. He condemned the abolition
as useless, unless other nations would take it up. He brought to the
recollection of the House the barbarous scenes which had taken place in St.
Domingo, all of which, he said, had originated in the discussion of this
question. He described the alarms, in which the inhabitants of our own
islands were kept, lest similar scenes should occur from the same cause. He
ridiculed the petitions on the table. Itinerant clergymen, mendicant
physicians, and others, had extorted signatures from the sick, the
indigent, and the traveller. School-boys were invited to sign them, under
the promise of a holiday. He had letters to produce, which would prove all
these things, though he was not authorized to give up the names of those
who had written them.
Mr. Montagu said, that, in the last session, he had simply entered his
protest against the trade; but now he could be no longer silent; and as
there were many, who had conceived regulation to be more desirable than
abolition, he would confine himself to that subject.
Regulation, as it related to the manner of procuring slaves, was utterly
impossible: for how could we know the case of each individual, whom we
forced away into bondage? Could we establish tribunals all along the coast,
and in every ship, to find it out? What judges could we get for such an
office? But, if this could not be done upon the coast, how could we
ascertain the justness of the captivity of by far the greatest number, who
were brought from immense distances inland?
He would not dwell upon the proof of the inefficiency of regulations, as to
the Middle Passage. His honourable friend Mr. Wilberforce had shown, that,
however the mortality might have been lessened in some ships by the
regulations of Sir William Dolben, yet, wherever a contagious disorder
broke out, the greatest part of the cargo was swept away. But what
regulations by the British Parliament could prevent these contagions, or
remove them suddenly, when they appeared?
Neither would regulations be effectual, as they related to the protection
of the slaves in the West Indies. It might perhaps be enacted, as Mr.
Vaughan had suggested, that their punishments should be moderate; and that
the number of lashes should be limited. But the colonial legislatures had
already done as much, as the magic of words alone could do, upon this
subject: yet the evidence upon the table clearly proved, that the only
protection of slaves was in the clemency of their masters. Any barbarity
might be exercised with impunity, provided no White person were to see it,
though it happened in the sight of a thousand slaves. Besides, by splitting
the offence, and inflicting the punishment at intervals, the law could be
evaded, although the fact was within the reach of the evidence of a White
man. Of this evasion, Captain Cook, of the eighty-ninth regiment, had given
a shocking instance: and Chief Justice Ottley had candidly confessed, that
"he could devise no method of bringing a master, so offending, to justice,
while the evidence of the slave continued inadmissible." But perhaps
councils of protection, and guardians of the slaves, might be appointed.
This again was an expedient, which sounded well; but which would be
nugatory and absurd. What person would risk the comfort of his life by the
exercise of so invidious an interference? But supposing that one or two
individuals could be found, who would sacrifice all their time, and the
friendship of their associates, for the good of the slaves; what could they
effect? Could they be in all places at once? But even if acts of barbarity
should be related to them, how were they to come at the proof of them?
It appeared then that no regulations could be effectual until the slaves
were admitted to give their evidence: but to admit them to this privilege
in their present state would be to endanger the safety and property of
their masters. Mr. Vaughan had, however, recommended this measure with
limitations, but it would produce nothing but discontent; for how were the
slaves to be persuaded, that it was fit they should be admitted to speak
the truth, and then be disbelieved and disregarded? What a fermentation
would such a conduct naturally excite in men dismissed with injuries
unredressed, though abundantly proved, in their apprehension, by their
testimony! In fact, no regulations would do. There was no cure for these
evils, but in the abolition of the Slave-trade. He called upon the planters
to concur with his honourable friend Mr. Wilberforce in this great measure.
He wished them to consider the progress, which the opinion of the injustice
of this trade was making in the nation at large, as manifested by the
petitions; which had almost obstructed the proceedings of the House by
their perpetual introduction. It was impossible for them to stifle this
great question. As for himself, he would renew his profession of last year,
that he would never cease, but with life, to promote so glorious an end.
Mr. Whitbread said, that even if he could conceive, that the trade was, as
some had asserted it to be, founded on principles of humanity; that the
Africans were rescued from death in their own country; that, upon being
carried to the West Indies, they were put under kind masters; that their
labour there was easy; that at evening they returned cheerful to their
homes; that in sickness they were attended with care; and that their old
age was rendered comfortable; even then he would vote for the abolition of
the Slave-trade; inasmuch as he was convinced, that that, which was
fundamentally wrong, no practice could justify.
No eloquence could persuade him, that the Africans were torn from their
country and their dearest connections, merely that they might lead a
happier life; or that they could be placed under the uncontrolled dominion
of others without suffering. Arbitrary power would spoil the hearts of the
best. Hence would arise tyranny on the one side, and a sense of injury on
the other. Hence the passions would be let loose, and a state of perpetual
enmity would follow.
He needed only to go to the accounts of those who defended the system of
slavery, to show that it was cruel. He was forcibly struck last year by an
expression of an honourable member, an advocate for the trade, who, when
he came to speak of the slaves, on selling off the stock of a plantation,
said, that they fetched less than the common price, because they were
damaged.--Damaged!--What! were they goods and chattels? What an idea was
this to hold out of our fellow-creatures. We might imagine how slaves were
treated, if they could be spoken of in such a manner. Perhaps these unhappy
people had lingered out the best part of their lives in the service of
their master. Able then to do but little, they were sold for little! and
the remaining substance of their sinews was to be pressed out by another,
yet more hardened than the former, and who had made a calculation of their
vitals accordingly.
As another proof, he would mention a passage in a pamphlet, in which the
author, describing the happy situation of the slaves, observed, that a good
Negro never wanted a character. A bad one could always be detected by his
weals and scars. What was this but to say, that there were instruments in
use, which left indelible marks behind them; and who would say, that these
were used justly?
An honourable gentleman, Mr. Vaughan, had said, that setting aside slavery,
the slaves were better off than the poor in this country. But what was it
that we wished to abolish? Was it not the Slave-trade, which would destroy
in time the cruel distinction he had mentioned? The same honourable
gentleman had also expressed his admiration of their resignation; but might
it not be that resignation, which was the consequence of despair?
Colonel Tarleton had insinuated, that the petitions on the table had been
obtained in an objectionable manner. He had the honour to present one from
his constituents; which he would venture to say had originated with
themselves; and that there did not exist more respectable names in the
kingdom, than those of the persons who had signed it. He had also asserted,
that there was a strong similitude in their tenour and substance, as if
they had been manufactured by the same persons. This was by no means to be
wondered at. There was surely but one plain tale to tell; and it was not
surprising, that it had been clothed in nearly the same expressions. There
was but one boon to ask, and that was--the abolition of this wicked trade.
It had been said by another, (Mr. Baillie) that the horrible insurrections
in St. Domingo arose from the discussion of the question of the
Slave-trade. He denied the assertion; and maintained that they were the
effect of the trade itself. There was a point of endurance, beyond which
human nature could not go; at which the mind of man rose by its native
elasticity with a spring and violence proportioned to the degree to which
it had been depressed. The calamities in St. Domingo proceeded from the
Slave-trade alone; and, if it were continued, similar evils were to be
apprehended in our own islands. The cruelties, which the slaves had
perpetrated in that unfortunate colony, they had learnt from their masters.
Had not an African eyes? Had he not ears? Had he not organs, senses, and
passions? If you pricked him, would he not feel the puncture and bleed? If
you poisoned him, would he not die? and, if you wronged him, would he not
revenge? But he had said sufficient; for he feared he could not better the
instruction.
Mr. Milbank would only just observe, that the policy of the measure of the
abolition was as great, as its justice was undeniable. Where slavery
existed, every thing was out of its natural place. All improvement was at
an end. There must also, from the nature of the human heart, be oppression.
He warned the planters against the danger of fresh importations, and
invited their concurrence in the measure.
Mr. Dundas (now Lord Melville) declared, that he had always been a warm
friend to the abolition of the Slave-trade, though he differed with Mr.
Wilberforce as to the mode of effecting it.
The abolitionists, and those on the opposite side of the question, had,
both of them, gone into extremes. The former were for the immediate and
abrupt annihilation of the trade. The latter considered it as essentially
necessary to the existence of the West Indian islands, and therefore laid
it down, that it was to be continued for ever. Such was the vast distance
between the parties. He would now address himself to each.
He would say first, that he agreed with his honourable friend Mr.
Wilberforce in very material points. He believed the trade was not founded
in policy; that the continuation of it was not essential to the
preservation of our trade with the West Indian islands; and that the slaves
were not only to be maintained, but increased there, by natural population.
He agreed, too, as to the propriety of the abolition. But when his
honourable friend talked of direct and abrupt abolition, he would submit it
to him, whether he did not run counter to the prejudices of those who were
most deeply interested in the question; and whether, if he could obtain his
object without wounding these, it would not be better to do it? Did he not
also forget the sacred attention, which Parliament had ever shown to the
private interests and patrimonial rights of individuals?
Whatever idea men might then have of the African trade, certain it was that
they, who had connected themselves with it, had done it under the sanction
of Parliament. It might also be well worth while to consider (though the
conduct of other nations ought not to deter us from doing our duty) whether
British subjects in the West Indies might not be supplied with slaves under
neutral flags. Now he believed it was possible to avoid these objections,
and at the same time to act in harmony with the prejudices which had been
mentioned. This might be done by regulations, by which we should effect the
end much more speedily than by the way proposed. By regulations, he meant
such as would increase the breed of the slaves in the West Indies; such as
would ensure a moral education to their children; and such as would even in
time extinguish hereditary slavery. The extinction, however, of this was
not to be effected by allowing the son of an African slave to obtain his
freedom on the death of his parent. Such a son should be considered as born
free. He should then be educated at the expense of the person importing his
parents; and, when arrived at such a degree of strength as might qualify
him to labour, he should work for a term of years for the payment of the
expense of his education and maintenance. It was impossible to emancipate
the existing slaves at once; nor would such an emancipation be of any
immediate benefit to themselves: but this observation would not apply to
their descendants, if trained and educated in the manner he had proposed.
He would now address himself to those who adopted the opposite extreme: and
he thought he should not assume too much, when he said, that if both
slavery and the Slave-trade could be abolished with safety to their
property, it deeply concerned their interests to do it. Such a measure,
also, would only be consistent with the principles of the British
Constitution. It was surely strange that we, who were ourselves free,
should carry on a Slave-trade with Africa; and that we should never think
of introducing cultivation into the West Indies by free labourers.
That such a measure would tend to their interest he had no doubt. Did not
all of them agree with Mr. Long, that the great danger in the West Indies
arose from the importation of the African slaves there? Mr. Long had
asserted, that all the insurrections there arose from these. If this
statement were true, how directly it bore upon the present question! But we
were told also, by the same author, that the Slave-trade gave rise to
robbery, murder, and all kinds of depredations on the coast of Africa. Had
this been answered? No: except indeed it had been said, that the slaves
were such as had been condemned for crimes. Well then: the imported
Africans consisted of all the convicts, rogues, thieves, and vagabonds in
Africa. But would the West Indians choose to depend on fresh supplies of
these for the cultivation of their lands, and the security of their
islands, when it was also found that every insurrection had arisen from
them? it was plain the safety of the islands was concerned in this
question. There would be danger so long as the trade lasted. The Planters
were, by these importations, creating the engines of their own destruction.
Surely they would act more to their own interest, if they would concur in
extinguishing the trade, than by standing up for its continuance.
He would now ask them, what right they had to suppose that Africa would for
ever remain in a state of barbarism. If once an enlightened prince were to
rise up there, his first act would be to annihilate the Slave-trade. If the
light of heaven were ever to descend upon that continent, it would directly
occasion its downfall. It was their interest then to contrive a mode of
supplying labour, without trusting to precarious importations from that
quarter. They might rest assured that the trade could not continue. He did
not allude to the voice of the people in the petitions then lying on the
table of the House; but he knew certainly, that an idea not only of the
injustice but of the impolicy of this trade had been long entertained by
men of the most enlightened understandings in this country. Was it then a
prudent thing for them to rest on this commerce for the further improvement
of their property?
There was a species of slavery, prevailing only a few years ago, in the
collieries in certain boroughs of Scotland. Emancipation there was thought
a duty by Parliament: But what an opposition there was to the measure!
Nothing but ruin would be the consequence of it! After several years
struggle the bill was carried. Within a year after, the ruin so much talked
of vanished in smoke, and there was an end of the business. It had also
been contended that Sir William Dolben's bill would be the ruin of
Liverpool: and yet one of its representatives had allowed, that this bill
had been of benefit to the owners of the slave-vessels there. Was he then
asking too much of the West Indians, to request a candid consideration of
the real ground of their alarms? He would conclude by stating, that he
meant to propose a middle way of proceeding. If there was a number of
members in the House, who thought with him, that this trade ought to be
ultimately abolished, but yet by moderate measures, which should neither
invade the property nor the prejudices of individuals; he wished them to
unite, and they might then reduce the question to its proper limits.
Mr. Addington (the speaker) professed himself to be one of those moderate
persons called upon by Mr. Dundas. He wished to see some middle measure
suggested. The fear of doing injury to the property of others, had hitherto
prevented him from giving an opinion against a system, the continuance of
which he could not countenance.
He utterly abhorred the Slave-trade. A noble and learned lord, who had now
retired from the bench, said on a certain occasion, that he pitied the
loyalty of that man, who imagined that any epithet could aggravate the
crime of treason. So he himself knew of no language which could aggravate
the crime of the Slave-trade. It was sufficient for every purpose of
crimination, to assert, that man thereby was bought and sold, or that he
was made subject to the despotism of man. But though he thus acknowledged
the justice due to a whole continent on the one side, he confessed there
were opposing claims of justice on the other. The case of the West Indians
deserved a tender consideration also.
He doubted, if we were to relinquish the Slave-trade alone, whether it
might not be carried on still more barbarously than at present; and
whether, if we were to stop it altogether, the islands could keep up their
present stocks. It had been asserted that they could. But he thought that
the stopping of the importations could not be depended upon for this
purpose, so much as a plan for providing them with more females.
With the mode suggested by his right honourable friend, Mr. Dundas, he was
pleased, though he did not wholly agree to it. He could not grant liberty
to the children born in the islands. He thought also, that the trade ought
to be permitted for ten or twelve years longer, under such arrangements as
should introduce a kind of management among the slaves there, favourable to
their interests, and of course to their future happiness. One species of
regulation which he should propose, would be greater encouragement to the
importation of females than of males, by means of a bounty on the former
till their numbers should be found equal. Rewards also might be given to
those slaves who should raise a certain number of children; and to those
who should devise means of lightening negro-labour. If the plan of his
honourable friend should comprehend these regulations, he would heartily
concur in it. He wished to see the Slave-trade abolished. Indeed it did not
deserve the name of a trade. It was not a trade, and ought not to be
allowed. He was satisfied, that in a few years it would cease to be the
reproach of this nation and the torment of Africa. But under regulations
like these, it would cease without any material injury to the interests of
others.
Mr. Fox said, that after what had fallen from the two last speakers he
could remain no longer silent. Something so mischievous had come out, and
something so like a foundation had been laid for preserving, not only for
years to come, but for ever, this detestable traffic, that he should feel
himself wanting in his duty, if he were not to deprecate all such
deceptions and delusions upon the country.
The honourable gentlemen had called themselves moderate men: but upon this
subject he neither felt, nor desired to feel, any thing like a sentiment of
moderation. Their speeches had reminded him of a passage in Middleton's
Life of Cicero. The translation of it was defective, though it would
equally suit his purpose. He says, "To enter into a man's house, and kill
him, his wife, and family, in the night, is certainly a most heinous crime,
and deserving of death; but to break open his house, to murder him, his
wife, and all his children, in the night, may be still very right, provided
it be done with moderation." Now, was there any thing more absurd in this
passage, than to say, that the Slave-trade might be carried on with
moderation; for, if you could not rob or murder a single man with
moderation, with what moderation could you pillage and wound a whole
nation? In fact, the question of the abolition was simply a question of
justice. It was only, whether we should authorize by law, respecting
Africa, the commission of crimes, for which, in this country, we should
forfeit our lives; notwithstanding which, it was to be treated, in the
opinion of these honourable gentlemen, with moderation.
Mr. Addington had proposed to cure the disproportion of the sexes in the
islands, by a bounty on the importation of females; or, in other words, by
offering a premium to any crew of ruffians, who would tear them from their
native country. He would let loose a banditti against the most weak and
defenceless of the sex. He would occasion these to kill fathers, husbands,
and brothers, to get possession of their relatives, the females, who, after
this carnage, were to be reserved for--slavery. He should like to see the
man, who would pen such a moderate clause for a British Parliament.
Mr. Dundas had proposed to abolish the Slave-trade, by bettering the state
of the slaves in the islands, and particularly that of their offspring. His
plan, with respect to the latter, was not a little curious. They were to
become free, when born; and then they were to be educated at the expense of
those to whom their fathers belonged. But it was clear, that they could not
be educated for nothing. In order, therefore, to repay this expense, they
were to be slaves for ten or fifteen years. In short, they were to have an
education, which was to qualify them to become freemen; and, after they had
been so educated, they were to become slaves. But as this free education
might possibly unfit them for submitting to slavery; so, after they had
been made to bow under the yoke for ten or fifteen years, they might then,
perhaps, be equally unfit to become free; and therefore, might be retained
as slaves for a few years longer, if not for their whole lives. He never
heard of a scheme so moderate, and yet so absurd and visionary.
The same honourable gentleman had observed, that the conduct of other
nations should not hinder us from doing our duty; but yet neutrals would
furnish our islands with slaves. What was the inference from this moderate
assertion, but that we might as well supply them ourselves? He hoped, if we
were yet to be supplied, it would never be by Englishmen. We ought no
longer to be concerned in such a crime.
An adversary, Mr. Baillie, had said, that it would not be fair to take the
character of this country from the records of the Old Bailey. He did not at
all wonder, when the subject of the Slave-trade was mentioned, that the Old
Bailey naturally occurred to his recollection. The facts which had been
described in the evidence, were associated in all our minds with the ideas
of criminal justice. But Mr. Baillie had forgot the essential difference
between the two cases. When we learnt from these records, that crimes were
committed in this country, we learnt also, that they were punished with
transportation and death. But the crimes committed in the Slave-trade were
passed over with impunity. Nay, the perpetrators were even sent out again
to commit others.
As to the mode of obtaining slaves, it had been suggested as the least
disreputable, that they became so in consequence of condemnation as
criminals. But he would judge of the probability of this mode by the
reasonableness of it. No less than eighty thousand Africans were exported
annually by the different nations of Europe from their own country. Was it
possible to believe, that this number could have been legally convicted of
crimes, for which they had justly forfeited their liberty? The supposition
was ridiculous. The truth was, that every enormity was practised to obtain
the persons of these unhappy people. He referred those present to the case
in the evidence of the African trader, who had kidnapped and sold a girl,
and who was afterwards kidnapped and sold himself. He desired them to
reason upon the conversation which had taken place between the trader and
the captain of the ship on this occasion. He desired them also to reason
upon the instance mentioned this evening, which had happened in the river
Cameroons, and they would infer all the rapine, all the desolation, and all
the bloodshed, which had been placed to the account of this execrable
trade.
An attempt had been made to impress the House with the horrible scenes
which had taken place in St. Domingo, as an argument against the abolition
of the Slave-trade; but could any more weighty argument be produced in its
favour? What were the causes of the insurrections there? They were two. The
first was the indecision of the National Assembly, who wished to compromise
between that which was right and that which was wrong on this subject. And
the second was the oppression of the People of Colour, and of the Slaves.
In the first of the causes we saw something like the moderation of Mr.
Dundas and Mr. Addington. One day this Assembly talked of liberty, and
favoured the Blacks. Another day they suspended their measures, and
favoured the Whites. They wished to steer a middle course; but decision had
been mercy. Decision even against the Planters would have been a thousand
times better than indecision and half measures. In the mean time, the
People of Colour took the great work of justice into their own hands.
Unable, however, to complete this of themselves, they called in the aid of
the Slaves. Here began the second cause; for the Slaves, feeling their own
power, began to retaliate on the Whites. And here it may be observed, that,
in all revolutions, the clemency or cruelty of the victors will always be
in proportion to their former privileges, or their oppression. That the
Slaves then should have been guilty of great excesses was not to be
wondered at; for where did they learn their cruelty? They learnt it from
those who had tyrannized over them. The oppression, which they themselves
had suffered, was fresh in their memories, and this had driven them to
exercise their vengeance so furiously. If we wished to prevent similar
scenes in our own islands, we must reject all moderate measures, and at
once abolish the Slave-trade. By doing this, we should procure a better
treatment for the Slaves there; and when this happy change of system should
have taken place, we might depend on them for the defence of the islands as
much as on the Whites themselves.
Upon the whole, he would give his opinion of this traffic in a few words.
He believed it to be impolitic--he knew it to be inhuman--he was certain it
was unjust--he though it so inhuman and unjust, that, if the colonies could
not be cultivated without it, they ought not to be cultivated at all. It
would be much better for us to be without them, than not abolish the
Slave-trade. He hoped therefore that members would this night act the part
which would do them honour. He declared, that, whether he should vote in a
large minority or a small one, he would never give up the cause. Whether in
the House of Parliament or out of it, in whatever situation he might ever
be, as long as he had a voice to speak, this question should never be at
rest. Believing the trade to be of the nature of crimes and pollutions,
which stained the honour of the country, he would never relax his efforts.
It was his duty to prevent man from preying upon man; and if he and his
friends should die before they had attained their glorious object, he hoped
there would never be wanting men alive to their duty, who would continue to
labour till the evil should be wholly done away. If the situation of the
Africans was as happy as servitude could make them, he could not consent to
the enormous crime of selling man to man; nor permit a practice to
continue, which put an entire bar to the civilization of one quarter of the
globe. He was sure that the nation would not much longer allow the
continuance of enormities which shocked human nature. The West Indians had
no right to demand that crimes should be permitted by this country for
their advantage; and, if they were wise, they would lend their cordial
assistance to such measures, as would bring about, in the shortest possible
time, the abolition of this execrable trade.
Mr. Dundas rose again, but it was only to move an amendment, namely, that
the word "gradually" should be inserted before the words "to be abolished"
in Mr. Wilberforce's motion.
Mr. Jenkinson (now Lord Hawkesbury) said, that the opinions of those who
were averse to the abolition had been unfairly stated. They had been
described as founded on policy, in opposition to humanity. If it could be
made out that humanity would be aided by the abolition, he would be the
last person to oppose it. The question was not, he apprehended, whether the
trade was founded in injustice and oppression. He admitted it was: nor was
it, whether it was in itself abstractedly an evil: he admitted this also:
but whether, under all the circumstances of the case, any considerable
advantage would arise to a number of our fellow-creatures from the
abolition of the trade in the manner in which it had been proposed.
He was ready to admit, that the Africans at home were made miserable by the
Slave-trade, and that, if it were universally abolished, great benefit
would arise to them. No one, however, would assert, that these miseries
arose from the trade as carried on by Great Britain only. Other countries
occasioned as much of the evil as we did; and if the abolition of it by us
should prove only the transferring of it to those countries, very little
benefit would result from the measure.
What then was the probability of our example being followed by foreign
powers? Five years had now elapsed since the question was first started,
and what had any of them done? The Portuguese continued the trade. The
Spaniards still gave a bounty to encourage it. He believed there were
agents from Holland in this country, who were then negotiating with persons
concerned in it in order to secure its continuance. The abolition also had
been proposed in the National Assembly of France, and had been rejected
there. From these circumstances he had a right to infer, that if we gave up
the trade, we should only transfer it to those countries: but this transfer
would be entirely against the Africans. The mortality on board English
ships, previously to the regulating bill, was four and an eighth per cent.
Since that time it had been reduced to little more than three per cent.[A]
In French ships it was near ten, and in Dutch ships from five to seven, per
cent. In Portuguese it was less than either in French or Dutch, but more
than in English ships since the regulating bill. Thus the deaths of the
Africans would be more than doubled, if we were to abolish the trade.
[Footnote A: Mr. Wilberforce stated it on the same evening to be between
ten and eleven per cent. for the last year. The number then exported from
Africa to our islands was rather more than 22,000, of whom more than 2,300
died.]
Perhaps it might be replied, that, the importations being stopped in our
own islands, fewer Africans would experience this misery, because fewer
would be taken from their own country on this account. But he had a right
to infer, that as the planters purchased slaves at present, they would
still think it their interest to have them. The question then was, whether
they could get them by smuggling. Now it appeared by the evidence, that
many hundred slaves had been stolen from time to time from Jamaica, and
carried into Cuba. But if persons could smuggle slaves out of our colonies,
they could smuggle slaves into them; but particularly when the planters
might think it to their interest to assist them.
With respect to the slaves there, instances had been related of their
oppression, which shocked the feelings of all who heard them: But was it
fair to infer from these their general ill usage? Suppose a person were to
make a collection of the different abuses, which had happened for a series
of years under our own happy constitution, and use these as an argument of
its worthlessness; should we not say to him, that in the most perfect
system which the human intellect could form, some defects would exist; and
that it was unfair to draw inferences from such partial facts? In the same
manner he would argue relative to the alleged treatment of the slaves.
Evidence had been produced upon this point on both sides. He should not be
afraid to oppose the authorities of Lord Rodney, and others, against any,
however respectable, in favour of the abolition. But this was not
necessary. There was another species of facts, which would answer the same
end. Previously to the year 1730 the decrease of the slaves in our islands
was very considerable. From 1730 to 1755 the deaths were reduced to only
two and a half per cent. above the births: from 1755 to 1768 to only one
and three fourths; and from 1768 to 1788 to only one per cent. This then,
on the first view of the subject, would show, that whatever might have been
the situation of slaves formerly, it had been gradually improved. But if,
in addition to this, we considered the peculiar disadvantages under which
they laboured; the small proportion of females to males; and the
hurricanes, and famines, which had swept away thousands, we should find it
physically impossible, that they could have increased as related, if they
had been treated as cruelly as the friends of the abolition had described.
This species of facts would enable him also to draw still more important
conclusions; namely, that as the slaves in the West Indies had gradually
increased, they would continue to increase; that very few years would pass,
not only before the births were equal to the deaths, but before they were
more numerous than the deaths; and that if this was likely to happen in the
present state of things, how much more would it happen, if by certain
regulations the increase of the slaves should be encouraged?
The only question then was, whether it was more advantageous to breed or to
import. He thought he should prove the former; and if so, then this
increase was inevitable, and the importations would necessarily cease.
In the first place, the gradual increase of the slaves of late years
clearly proved, that such increase had been encouraged. But their price had
been doubled in the last twenty years. The planter therefore must feel it
his interest to desist from purchasing, if possible. But again, the
greatest mortality was among the newly imported slaves. The diseases they
contracted on the passage, and their deaths in the seasoning, all made for
the same doctrine. Add to this, that slaves bred in the islands were more
expert at colonial labour, more reconciled to their situation, and better
disposed towards their masters, than those who were brought from Africa.
But it had been said, that the births and deaths in the islands were now
equal; and, that therefore no further supply was wanted. He denied the
propriety of this inference. The slaves were subject to peculiar diseases.
They were exposed also to hurricanes and consequent famines. That the day,
however, would come, when the stock there would be sufficient, no person
who attended to the former part of his argument could doubt. That they had
gradually increased, were gradually, increasing, and would, by certain
regulations, increase more and more, must be equally obvious. But these
were all considerations for continuing the traffic a little longer.
He then desired the House to reflect upon the state of St. Domingo. Had not
its calamities been imputed by its own deputies to the advocates for the
abolition? Were ever any scenes of horror equal to those which had passed
there? And should we, when principles of the same sort were lurking in our
own islands, expose our fellow-subjects to the same miseries, who, if
guilty of promoting this trade, had, at least, been encouraged in it by
ourselves?
That the Slave-trade was an evil, he admitted. That the state of slavery
itself was likewise an evil, he admitted; and if the question was, not
whether we should abolish, but whether we should establish these, he would
be the first to oppose himself to their existence; but there were many
evils, which we should have thought it our duty to prevent, yet which, when
they had once arisen, it was more dangerous to oppose than to submit to.
The duty of a statesman was, to consider abstractedly what was right or
wrong, but to weigh the consequences which were likely to result from the
abolition of an evil, against those, which were likely to result from its
continuance. Agreeing then most perfectly with the abolitionists in their
end, he differed from them only in the means of accomplishing it. He was
desirous of doing that gradually, which he conceived they were doing
rashly. He had therefore drawn up two propositions. The first was, That an
address be presented to His Majesty, that he would recommend to the
colonial assemblies to grant premiums to such planters, and overseers, as
should distinguish themselves by promoting the annual increase of the
slaves by birth; and likewise freedom to every female slave, who had reared
five children to the age of seven years. The second was, That a bounty of
five pounds per head be given to the master of every slave-ship, who should
import in any cargo a greater number of females than males, not exceeding
the age of twenty-five years. To bring forward these propositions, he would
now move that the chairman leave the chair.
Mr. Este wished the debate to be adjourned. He allowed there ware many
enormities in the trade, which called for regulation. There were two
propositions before the House: the one for the immediate, and the other for
the gradual, abolition of the trade. He thought that members should be
allowed time to compare their respective merits. At present his own opinion
was, that gradual abolition would answer the end proposed in the least
exceptionable manner.
Mr. Pitt rejoiced that the debate had taken a turn, which contracted the
question into such narrow limits. The matter then in dispute was merely as
to the time at which the abolition should take place. He therefore
congratulated the House, the country, and the world, that this great point
had been gained; that we might now consider this trade as having received
its condemnation; that this curse of mankind was seen in its true light;
and that the greatest stigma on our national character, which ever yet
existed, was about to be removed! Mankind, he trusted, were now likely to
be delivered from the greatest practical evil that ever afflicted the human
race--from the most severe and extensive calamity recorded in the history
of the world.
His honourable friend (Mr. Jenkinson) had insinuated, that any act for the
abolition would be evaded. But if we were to enforce this act with all the
powers of the country, how could it fail to be effectual? But his
honourable friend had himself satisfied him upon this point. He had
acknowledged, that the trade would drop of itself, on account of the
increasing dearness of the commodity imported. He would ask then, if we
were to leave to the importer no means of importation but by smuggling; and
if, besides all the present disadvantages, we were to load him with all the
charges and hazards of the smuggler, would there be any danger of any
considerable supply of fresh slaves being poured into the islands through
this channel? The question under these circumstances, he pronounced, would
not bear a dispute.
His honourable friend had also maintained, that it would be inexpedient to
stop the importations immediately, because the deaths and births in the
islands were as yet not equal. But he (Mr. Pitt) had proved last year, from
the most authentic documents, that an increase of the births above the
deaths had already taken place. This then was the time for beginning the
abolition. But he would now observe, that five years had elapsed since
these documents were framed; and therefore the presumption was, that the
Black population was increasing at an extraordinary rate. He had not, to be
sure, in his consideration of the subject, entered into the dreadful
mortality arising from the clearing of new lands. Importations for this
purpose were to be considered, not as carrying on the trade, but as setting
on foot a Slave-trade, a measure which he believed no one present would
then support. He therefore asked his honourable friend, whether the period
he had looked to was now arrived? whether the West Indies, at this hour,
were not in a state, in which they could maintain their population?
It had been argued, that one or other of these two assertions was false;
that either the population of the slaves must be decreasing, (which the
abolitionists denied,) or, if it was increasing, the slaves must have been
well treated. That their population was rather increasing than otherwise,
and also that their general treatment was by no means so good as it ought
to have been, were both points which had been proved by different
witnesses. Neither were they incompatible with each other. But he would see
whether the explanation of this seeming contradiction would not refute the
argument of expediency, as advanced by his honourable friend. Did the
slaves decrease in numbers?--Yes. Then ill usage must have been the cause
of it; but if so, the abolition was immediately necessary to restrain it.
Did they, on the other hand, increase?--Yes. But if so, no further
importations were wanted: Was their population (to take a middle course)
nearly stationary, and their treatment neither so good nor so bad as it
might be?--Yes. But if so, this was the proper period for stopping further
supplies; for both the population and the treatment would be improved by
such a measure.
But he would show again the futility of the argument of his honourable
friend. He himself had admitted, that it was in the power of the colonists Negros were allowed the
afternoons it had not yet.
He would now try this argument of expediency by other considerations. The
best informed writers on the subject had told us, that the purchase of new
Negros was injurious to the planters. But if this statement was just, would
not the abolition be beneficial to them? That it would, was the opinion of
Mr. Long, their own historian. "If the Slave-trade," says he, "was
prohibited for four or five years, it would enable them, to retrieve their
affairs by preventing them from running into debt, either by renting or
purchasing Negros." To this acknowledgment he would add a fact from the
evidence, which was, that a North American province, by such a prohibition
alone for a few years, from being deeply plunged in debt, had become
independent, rich, and flourishing.
The next consideration was the danger, to which the islands were exposed
from the newly imported slaves. Mr. Long, with a view of preventing
insurrections, had advised, that a duty, equal to a prohibition, might be
laid on the importation of Coromantine slaves. After noticing one
insurrection, which happened through their means, he speaks of another in
the following year, in which thirty-three Coromantines, "most of whom had
been newly imported, murdered and wounded no less than nineteen Whites in
the space of an hour." To the authority of Mr. Long he would add the
recorded opinion of a Committee of the House of Assembly of Jamaica, which
was appointed to inquire into the best means of preventing future
insurrections. The Committee reported, that "the rebellion had originated,
like most others, with the Coromantines," and they proposed that a bill
should be brought in for laying a higher duty on the importation of these
particular Negros, which should operate as a prohibition. But the danger
was not confined to the introduction of Coromantines. Mr. Long accounts for
the frequent insurrections in Jamaica from the greatness of its general
importations. "In two years and a half," says he, "twenty-seven thousand
Negros have been imported--No wonder that we have rebellions!" Surely then,
when his honourable friend spoke of the calamities of St. Domingo, and of
similar dangers impending over our own islands, it ill became him to be the
person to cry out for further importations! It ill became him to charges
upon the abolitionists the crime of stirring up insurrections, who only
recommended what the Legislature of Jamaica itself had laid down in a time
of danger with an avowed view to prevent them. It was indeed a great
satisfaction to himself, that among the many arguments for prohibiting the
Slave-trade, the security of our West Indian possessions against internal
commotions, as well as foreign enemies, was among the most prominent and
forcible. And here he would ask his honourable friend, whether in this part
of the argument he did not see reason for immediate abolition. Why should
we any longer persist in introducing those latent principles of
conflagration, which, if they should once burst forth, might annihilate the
industry of a hundred years? which might throw the planters back a whole
century in their profits, in their cultivation, and in their progress
towards the emancipation of their slaves? It was our duty to vote, that the
abolition of the Slave-trade should be immediate, and not to leave it to he
knew not what future time or contingency.
Having now done with the argument of expediency, he would consider the
proposition of his right honourable friend Mr. Dundas; that, on account of
some patrimonial rights of the West Indians, the prohibition of the
Slave-trade would be an invasion of their legal inheritance. He would first
observe, that, if this argument was worth any thing, it applied just as
much to gradual as to immediate abolition. He had no doubt, that, at
whatever period we should say the trade should cease, it would be equally
set up; for it would certainly be just as good an argument against the
measure in seventy years hence, as it was against it now. It implied also,
that Parliament had no right to stop the importations: but had this
detestable traffic received such a sanction, as placed it more out of the
jurisdiction of the legislature for ever after, than any other branch of
our trade? In what a situation did the proposition of his honourable friend
place the legislature of Great Britain! It was scarcely possible to lay a
duty on any one article, which might not in some way affect the property of
individuals.?
But he would appeal to the acts themselves. That of 23 George II. c. 31,
was the one upon which the greatest stress was laid. How would the House be
surprised to hear, that the very outrages committed in the prosecution of
this trade had been forbidden by that act! "No master of a ship trading to
Africa," says the act, "shall by fraud, force, or violence, or by any
indirect practice whatever, take on board or carry away from that coast any
Negro, or native of that country, or commit any violence on the natives, to
the prejudice of the said trade; and every person so offending, shall for
every such offence forfeit one hundred pounds." But the whole trade had
been demonstrated to be a system of fraud, force, and violence; and
therefore the contract was daily violated, under which the Parliament
allowed it to continue.
But why had the trade ever been permitted at all? The preamble of the act
would show: "Whereas the trade to and from Africa is very advantageous to
Great Britain, and necessary for supplying the Plantations and Colonies
thereunto belonging with a sufficient number of Negros at reasonable rates,
and for that purpose the said trade should be carried on"--Here then we
might see what the Parliament had in view, when it passed this act. But no
one of the occasions, on which it grounded its proceedings, now existed. He
would plead, then, the act itself as an argument for the abolition. If it
had been proved that, instead of being very advantageous to Great Britain,
it was the most destructive to her interests--that it was the ruin of her
seamen--that it stopped the extension of her manufactures;--if it had been
proved, in the second place, that it was not now necessary for the supply
of our Plantations with Negros;--if it had been further established, that
it was from the beginning contrary to the first principles of justice, and
consequently that a pledge for its continuance, had one been attempted to
be given, must have been absolutely void--where in this act of parliament
was the contract to be found, by which Britain was bound, as she was said
to be, never to listen to her own true interests and to the cries of the
natives of Africa? Was it not clear, that all argument, founded on the
supposed pledge of Parliament, made against those who employed it?
But if we were not bound by existing laws to the support of this trade, we
were doubly criminal in pursuing it: for why ought it to be abolished at
all? Because it was incurable injustice. Africa was the ground, on which he
chiefly rested; and there it was, that his two honourable friends, one of
whom had proposed gradual abolition, and the other regulation, did not
carry their principles to their full extent. Both had confessed the trade
to be a moral evil. How much stronger then was the argument for immediate
than for gradual abolition! If on the ground of a moral evil it was to be
abolished at last, why ought it not now? Why was injustice to be suffered
to remain for a single hour? He knew of no evil, which ever had existed,
nor could he imagine any to exist, worse than the tearing of eighty
thousand persons annually from their native land, by a combination of the
most civilized nations, in the most enlightened quarter of the globe; but
more especially by that nation, which called herself the most free and the
most happy of them all.
He would now notice the objection, that other nations would not give up the
Slave-trade, if we were to renounce it. But if the trade were stained but
by a thousandth part of the criminality, which he and others, after a
thorough investigation of the subject, charged upon it, the House ought
immediately to vote its abolition. This miserable argument, if persevered
in, would be an eternal bar to the annihilation of the evil. How was it
ever to be eradicated, if every nation was thus prudentially to wait till
the concurrence of all the world should be obtained? But it applied a
thousand times more strongly in a contrary way. How much more justly would
other nations say, "Great Britain, free as she is, just and honourable as
she is, not only has not abolished, but has refused to abolish, the
Slave-trade. She has investigated it well. Her senate has deliberated upon
it. It is plain, then, that she sees no guilt in it." With this argument we
should furnish the other nations of Europe, if we were again to refuse to
put an end to this cruel traffic: and we should have from henceforth not
only to answer for our own, but for their crimes also. Already we had
suffered one year to pass away; and now, when the question was renewed, not
only had this wretched argument been revived, but a proposition had been
made for the gradual abolition of the trade. He knew indeed the difficulty
of reforming long established abuses: but in the present case, by proposing
some other period than the present, by prescribing some condition, by
waiting for some contingency, perhaps till we obtained the general
concurrence of Europe, (a concurrence which he believed never yet took
place at the commencement of any one improvement in policy or morals,) he
feared that this most enormous evil would never be redressed. Was it not
folly to wait for the stream to run down before we crossed the bed of its
channel? Alas! we might wait for ever. The river would still flow on. We
should be no nearer the object, which we had in view, so long as the step,
which could alone bring us to it, was not taken.
He would now proceed to the civilization of Africa; and as his eye had just
glanced upon a West Indian law in the evidence upon the table, he would
begin with an argument, which the sight of it had suggested to him. This
argument had been ably answered in the course of the evening; but he would
view it in yet another light. It had been said, that the savage disposition
of the Africans rendered the prospect of their civilization almost
hopeless. This argument was indeed of long standing; but, last year, it had
been supported upon a new ground. Captain Frazer had stated in his
evidence, that a boy had been put to death at Cabenda, because there were
those who refused to purchase him as a slave. This single story was deemed
by him, and had been considered by others, as a sufficient proof of the
barbarity of the Africans, and of the inutility of abolishing the
Slave-trade. But they, who had used this fact, had suppressed several
circumstances relating to it. It appeared, on questioning Captain Frazer
afterward, that this boy had previously run away from his master three
several times; that the master had to pay his value, according to the
custom of the country, every time he was brought back; and that partly from
anger at the boy for running away so frequently, and partly to prevent a
repetition of the same expense, he determined to destroy him. Such was the
explanation of the signal instance, which was to fix barbarity on all
Africa, as it came out in the cross-examination of Captain Frazer. That
this African master was unenlightened and barbarous, he freely admitted:
but what would an enlightened and civilized West Indian have done in a
similar case? He would quote the law, passed in the West Indies in 1722,
which he had just cast his eye upon in the book of evidence, by which law
this very same crime of running away was by the legislature of an island,
by the grave and deliberate sentence of an enlightened legislature,
punished with death; and this, not in the case only of the third offence,
but even in the very first instance. It was enacted, "That, if any Negro or
other slave should withdraw himself from his master for the term of six
months; or any slave, who was absent, should not return within that time,
every such person should suffer death." There was also another West Indian
law, by which every Negro was armed against his fellow-negro, for he was
authorized to kill every runaway slave; and he had even a reward held out
to him for so doing. Let the House now contrast the two cases. Let them ask
themselves which of the two exhibited the greater barbarity; and whether
they could possibly vote for the continuance of the Slave-trade, upon the
principle, that the Africans had shown themselves to be a race of
incorrigible barbarians?
Something like an opposite argument, but with a like view, had been
maintained by others on this subject. It had been said, in justification of
the trade, that the Africans had derived some little civilization from
their intercourse with us. Yes: we had given them just enough of the forms
of justice to enable them to add the pretext of legal trials to their other
modes of perpetrating the most atrocious crimes. We had given them just
enough of European improvements, to enable them the more effectually to
turn Africa into a ravaged wilderness. Alas! alas! we had carried on a
trade with them from this civilized and enlightened country, which, instead
of diffusing knowledge, had been a check to every laudable pursuit. We had
carried a poison into their country, which spread its contagious effects
from one end of it to the other, and which penetrated to its very centre,
corrupting every part to which it reached. We had there subverted the whole
order of nature; we had aggravated every natural barbarity, and furnished
to every man motives for committing, under the name of trade, acts of
perpetual hostility and perfidy against his neighbour. Thus had the
perversion of British commerce carried misery instead of happiness to one
whole quarter of the globe. False to the very principles of trade,
misguided in our policy, unmindful of our duty, what almost irreparable
mischief had we done to that continent! How should we hope to obtain
forgiveness from Heaven, if we refused to use those means, which the mercy
of Providence had still reserved to us for wiping away the guilt and shame,
with which we were now covered? If we refused even this degree of
compensation, how aggravated would be our guilt! Should we delay, then, to
repair these incalculable injuries? We ought to count the days, nay the
very hours, which intervened to delay the accomplishment of such a work.
On this great subject, the civilization of Africa, which, he confessed, was
near his heart, he would yet add a few observations. And first he would
say, that the present deplorable state of that country, especially when we
reflected that her chief calamities were to be ascribed to us, called for
our generous aid, rather than justified any despair, on our part, of her
recovery, and still less a repetition of our injuries. On what ground of
theory or history did we act, when we supposed that she was never to be
reclaimed? There was a time, which it might be now fit to call to
remembrance, when human sacrifices, and even, this very practice of the
Slave-trade, existed in our own island. Slaves, as we may read in Henry's
History of Great Britain, were formerly an established article of our
exports. "Great numbers," he says, "were exported, like cattle, from the
British coast, and were to be seen exposed for sale in the Roman
market."--"Adultery, witchcraft, and debt," says the same historian, "were
probably some of the chief sources of supplying the Roman market with
British slaves--prisoners taken in war were added to the number--there
might be also among them some unfortunate gamesters, who, after having lost
all their goods, at length, staked themselves, their wives, and their
children." Now every one of these sources of slavery had been stated to be
at this hour a source of slavery in Africa. If these practices, therefore,
were to be admitted as proofs of the natural incapacity of its inhabitants,
why might they not have been applied to ancient Britain? Why might not then
some Roman senator, pointing to British barbarians, have predicted with
equal boldness, that these were a people, who were destined never to be
free; who were without the understanding necessary for the attainment of
useful arts; depressed by the hand of Nature below the level of the human
species; and created to form a supply of slaves for the rest of the world?
But happily, since that time, notwithstanding what would then have been the
justness of these predictions, we had emerged from barbarism. We were now
raised to a situation, which exhibited a striking contrast to every
circumstance, by which a Roman might have characterized us, and by which we
now characterized Africa. There was indeed one thing wanting to complete
the contrast, and to clear us altogether from the imputation of acting even
to this hour as barbarians; for we continued to this hour a barbarous
traffic in slaves. We continued it even yet, in spite of all our great
pretensions. We were once as obscure among the nations of the earth, as
savage in our manners, as debased in our morals, as degraded in our
understandings, as these unhappy Africans. But in the lapse of a long
series of years, by a progression slow, and for a time almost
imperceptible, we had become rich in a variety of acquirements. We were
favoured above measure in the gifts of Providence, we were unrivalled in
commerce, preeminent in arts, foremost in the pursuits of philosophy and
science, and established in all the blessings of civil society: we were in
the possession of peace, of liberty, and of happiness: we were under the
guidance of a mild and a beneficent religion; and we were protected by
impartial laws, and the purest administration of justice: we were living
under a system of government, which our own happy experience led us to
pronounce the best and wisest, and which had become the admiration of the
world. From all these blessings we must for ever have been excluded, had
there been any truth in those principles, which some had not hesitated to
lay down as applicable to the case of Africa; and we should have been at
this moment little superior, either in morals, knowledge, or refinement, to
the rude inhabitants of that continent.
If then we felt that this perpetual confinement in the fetters of brutal
ignorance would have been the greatest calamity which could have befallen
us; if we viewed with gratitude the contrast between our present and our
former situation; if we shuddered to think of the misery, which would still
have overwhelmed us, had our country continued to the present times,
through some cruel policy, to be the mart for slaves to the more civilized
nations of the world;--God forbid, that we should any longer subject Africa
to the same dreadful scourge, and exclude the sight of knowledge from her
coasts, which had reached every other quarter of the globe!
He trusted we should no longer continue this commerce; and that we should
no longer consider ourselves as conferring too great a boon on the natives
of Africa in restoring them to the rank of human beings. He trusted we
should not think ourselves too liberal, if, by abolishing the Slave-trade,
we gave them the same common chance of civilization with other parts of the
world. If we listened to the voice of reason and duty this night, some of
us might live to see a reverse of that picture, from which we now turned
our eyes with shame. We might live to behold the natives engaged in the
calm occupations of industry, and in the pursuit of a just commerce. We
might behold the beams of science and philosophy breaking in upon their
land, which at some happy period in still later times might blaze with full
lustre; and joining their influence to that of pure religion, might
illuminate and invigorate the most distant extremities of that immense
continent. Then might we hope, that even Africa (though last of all the
quarters of the globe) should enjoy at length, in the evening of her days,
those blessings, which had descended so plentifully upon us in a much
earlier period of the world. Then also would Europe, participating in her
improvement and prosperity, receive an ample recompense for the tardy
kindness (if kindness it could be called) of no longer hindering her from
extricating herself out of the darkness, which, in other more fortunate
regions, had been so much more speedily dispelled.
--Nos primus equis Oriens afflavit anhelis;
Illic sera rubens accendit lumina Vesper.
Then might be applied to Africa those words, originally used indeed with a
different view:
Hic demum exactis ---- ----
Devenere locos laetos, et amoena vireta
Fortunatorum nemorum, sedesque beatas;
Largior hic campos aether et lumine vestit
Purpurco:
It was in this view--it was as an atonement for our long and cruel
injustice towards Africa, that the measure proposed by his honourable
friend Mr. Wilberforce most forcibly recommended itself to his mind. The
great and happy change to be expected in the state of her inhabitants was,
of all the various benefits of the abolition, in his estimation the most
extensive and important. He should vote against the adjournment; and he
should also oppose every proposition, which tended either to prevent, or
even to postpone for an hour, the total abolition of the Slave-trade.
Mr. Pitt having concluded his speech (at about six in the morning), Sir
William Dolben, the chairman, proposed the following questions. The first
was on the motion of Mr. Jenkinson, "that the chairman do now leave the
chair." This was lost by a majority of two hundred and thirty-four to
eighty-seven. The second was on the motion of Mr. Dundas, "that the
abolition should be gradual;" when the votes for gradual exceeded those for
immediate by one hundred and ninety-three to one hundred and twenty-five.
He then put the amended question, that "it was the opinion of the
committee, that the trade ought to be gradually abolished." The committee
having divided again, the votes for a gradual abolition were two hundred
and thirty, and those against any abolition were eighty-five.
After this debate, the committee for the abolition of the Slave-trade held
a meeting. They voted their thanks to Mr. Wilberforce for his motion, and
to Mr. Pitt, Mr. Fox, and those other members of the House, who had
supported it. They resolved also, that the House of Commons, having
determined that the Slave-trade ought to be gradually abolished, had by
that decision manifested their opinion, that it was cruel and unjust. They
resolved also, that a gradual abolition of it was not an adequate remedy
for its injustice and cruelty; neither could it be deemed a compliance with
the general wishes of the people, as expressed in their numerous and urgent
petitions to Parliament. And they resolved lastly, that the interval, in
which the Slave-trade should be permitted to continue, afforded a prospect
of redoubled cruelties and ravages on the coast of Africa; and that it
imposed therefore an additional obligation on every friend to the cause to
use all constitutional means to obtain its immediate abolition.
At a subsequent meeting they voted their thanks to the right honourable
Lord Muncaster, for the able support he had given to the great object of
their institution by his Historical Sketches of the Slave-trade, and of its
Effects in Africa, addressed to the People of Great Britain; and they
elected the Reverend Richard Gifford and the Reverend Thomas Gisborne
honorary and corresponding members; the first on account of his excellent
sermon before mentioned and other services, and the latter on account of
his truly Christian and seasonable pamphlet, entitled Remarks on the late
Decision of the House of Commons respecting the Abolition of the
Slave-trade.
On the twenty-third of April, the House of Commons resolved itself into a
committee of the whole House, to consider the subject again; and Mr.
Beaufoy was put into the chair.
Mr. Dundas, upon whom the task of introducing a bill for the gradual
abolition of the Slave-trade now devolved, rose to offer the outlines of a
plan for that purpose. He intended, he said, immediately to abolish that
part of the trade, by which we supplied foreigners with slaves. The other
part of it was to be continued seven years from the first of January next.
He grounded the necessity of its continuance till this time upon the
documents of the Negro-population in the different islands. In many of
these, slaves were imported, but they were re-exported nearly in equal
numbers. Now all these he considered to be in a state to go on without
future supplies from Africa. Jamaica and the ceded islands retained almost
all the slaves imported into them. This he considered as a proof that these
had not attained the same desirable state; and it was therefore necessary,
that the trade should be continued longer on this account.
It was his intention, however, to provide proper punishments, while it
lasted, for abuses both in Africa and the Middle Passage. He would take
care, as far as he could, that none but young slaves should be brought from
the Coast of Africa. He would encourage establishments there for a new
species of traffic. Foreign nations should be invited to concur in the
abolition. He should propose a praedial rather than a personal service for
the West Indies, and institutions, by which the slaves there should be
instructed in religious duties. He concluded by reading several
resolutions, which he would leave to the future consideration of the House.
Mr. Pitt then rose. He deprecated the resolutions altogether. He denied
also the inferences, which Mr. Dundas had drawn from the West-Indian
documents relative to the Negro-population. He had looked over his own
calculations from the same documents again and again, and he would submit
them, with all their data, if it should be necessary, to the House.
Mr. Wilberforce and Mr. Fox held the same language. They contended also,
that Mr. Dundas had now proved, a thousand times more strongly than ever,
the necessity of immediate abolition. All the resolutions he had read were
operative against his own reasoning. The latter observed, that the
Slave-traders were in future only to be allowed to steal innocent children
from their disconsolate parents.
After a few observations by Lord Sheffield, Mr. Drake, Colonel Tarleton,
and Mr. Rolle, the House adjourned.
On the twenty-fifth of April it resumed the consideration of the subject.
Mr. Dundas then went over his former resolutions, and concluded by moving,
"that it should not be lawful to import any African Negros into any British
colonies, in ships owned or navigated by British subjects, at any time
after the first of January 1800."
Lord Mornington (now Marquis Wellesley) rose to propose an amendment. He
congratulated his countrymen, that the Slave-trade had received its
death-wound. This traffic was founded in injustice; and between right and
wrong there could be no compromise. Africa was not to be sacrificed to the
apparent good of the West-Indies. He would not repeat those enormities out
of the evidence, which had made such a deep impression upon the House. It
had been resolved, that the trade should be abolished. The question then
was, how long they were to persevere in the crime of its continuance. One
had said, that they might be unjust for ten years longer; another, only
till the beginning of the next century. But this diversity of opinion had
proceeded from an erroneous statement of Mr. Dundas against the clear and
irrefragable calculations of Mr. Pitt. The former had argued, that, because
Jamaica and the ceded islands had retained almost all the slaves which had
been imported into them, they were therefore not yet in a situation to
support their population without further supplies from Africa. But the
truth was, that the slaves, so retained, were kept, not to maintain the
population there, but to clear new land. Now the House had determined, that
the trade was not to be continued for this purpose. The population,
therefore, in the islands was sufficient to continue the ordinary
cultivation of them.
He deprecated the idea, that the Slave-trade had been so sanctioned by the
acts of former parliaments, that the present could make no alteration in
it. Had not the House altered the import of foreign sugar into our islands?
a measure, which at the time affected the property of many. Had they not
prohibited the exports of provisions from America to the same quarter?
Again, as to compacts, had the Africans ever been parties to these? It was
rather curious also, when King James the Second gave a charter to the
slave-traders, that he should have given them a right to all the south of
Africa, and authority over every person born therein! But, by doing this,
it was clear, that he gave them a right which he never possessed himself.
After many other observations, he concluded by moving, "that the year 1793
be substituted in the place of the year 1800."
In the course of the debate, which followed, Mr. Burdon stated his
conviction of the necessity of immediate abolition; but he would support
the amendment, as the shortest of the terms proposed.
Mr. Robert Thornton would support it also, as the only choice left him. He
dared not accede to a motion, by which we were to continue for seven years
to imbrue our hands in innocent blood.
Mr. Ryder would not support the trade for one moment, if he could avoid it.
He could not hold a balance with gold in one scale, and blood in the other.
Mr. William Smith exposed the wickedness of restricting the trade to
certain ages. The original motion, he said, would only operate as a
transfer of cruelty from the aged and the guilty to the young and the
innocent. He entreated the House to consider, whether, if it related to
their own children, any one of them would vote for it.
Mr. Windham had hitherto felt a reluctance to speaking, not from the
abstruseness, but from the simplicity, of the subject; but he could not
longer be silent, when he observed those arguments of policy creeping again
out of their lurking-places, which had fled before eloquence and truth. The
House had clearly given up the policy of the question. They had been
determined by the justice of it. Why were they then to be troubled again
with arguments of this nature? These, if admitted, would go to the
subversion of all public as well as private morality. Nations were as much
bound as individuals to a system of morals, though a breach in the former
could not be so easily punished. In private life morality took pretty good
care of itself. It was a kind of retail article, in which the returns were
speedy. If a man broke open his neighbour's house, he would feel the
consequences. There was an ally of virtue, who rendered it the interest of
individuals to be moral, and he was called the executioner. But as such
punishment did not always await us in our national concerns, we should
substitute honour as the guardian of our national conduct. He hoped the
West-Indians would consider the character of the mother-country, and the
obligations to national as well as individual justice. He hoped also they
would consider the sufferings, which they occasioned both in Africa, in the
passage, and in the West-Indies. In the passage indeed no one was capable
of describing them. The section of the slave-ship, however, made up the
deficiency of language, and did away all necessity of argument, on this
subject. Disease there had to struggle with the new affliction of chains
and punishment. At one view were the irksomeness of a gaol, and the
miseries of an hospital; so that the holds of these vessels put him in mind
of the regions of the damned. The trade, he said, ought immediately to be
abolished. On a comparison of the probable consequences of the abolition of
it, he saw on one side only doubtful contingencies, but on the other shame
and disgrace.
Sir James Johnstone contended for the immediate abolition of the trade. He
had introduced the plough into his own plantation in the West Indies, and
he found the land produced more sugar than when cultivated in the ordinary
way by slaves. Even for the sake of the planters, he hoped the abolition
would not be long delayed.
Mr. Dundas replied: after which a division took place. The number of votes
in favour of the original motion were one hundred and fifty-eight, and for
the amendment one hundred and nine.
On the 27th of April the House resumed the subject. Mr. Dundas moved, as
Back to
Full Books | http://www.fullbooks.com/The-History-of-the-Rise-Progress-andx18654.html | CC-MAIN-2017-17 | refinedweb | 22,107 | 65.86 |
FEA class for virtual (logical) interface state.
More...
#include <iftree.hh>
List of all members.
FEA class for virtual (logical) interface state.
Add IPv4 address.
Add IPv6 address.
Add recursively a new IPv4 address.
Add recursively a new IPv6 address.
Copy recursively from another vif.
Find a const IPv4 address.
Find an IPv6 address.
Find an IPv4 address.
Find a const IPv6 address.
[inline]
Test if the vif-specific internal state is same.
Mark IPv6 address as DELETED.
Deletion occurs when finalize_state is called.
Mark IPv4 address as DELETED.
Store the system-specific vif flags.
Typically, this value is read from the underlying system, and is used only for internal purpose.
Get the system-specific vif flags. | http://xorp.org/releases/current/docs/kdoc/html/classIfTreeVif.html | CC-MAIN-2017-30 | refinedweb | 117 | 65.49 |
2.7.:
- Programmatic Configuration Generation
- Collapse Request Functions
- Builder Priority Functions
- Build Priority Functions
canStartBuildFunctions
- Customizing SVNPoller
- Writing Change Sources
- Writing a New Latent Worker Implementation
- Custom Build Classes
- Factory Workdir Functions
- Writing New BuildSteps
- Writing Dashboards with Flask or Bottle
- A Somewhat Whimsical Example (or “It’s now customized, how do I deploy it?”)
If you’d like to clean it up, fork the project on GitHub and get started!
2.7.1._workers = ["worker%s" % n for n in range(10)] for python in pythons: f = util.BuildFactory() f.addStep(steps.SVN(...)) f.addStep(steps.ShellCommand(command=[python, 'test.py'])) c['builders'].append(util.BuilderConfig( name="test-%s" % python, factory=f, workernames=pytest_workers))
Next step would be the loading of
pythons list from a .yaml/.ini file.
2.7.2. Collapse Request Functions¶
The logic Buildbot uses to decide which build request can be merged can be customized by providing a Python function (a callable) instead of
True or
False described in Collapsing Build Requests.
Arguments for the callable are:
-
master
- pointer to the master object, which can be used to make additional data api calls via master.data.get
-
builder
- dictionary of type
builder
-
req1
- dictionary of type
buildrequest
-
req2
- dictionary of type
buildrequest
Warning
The number of invocations of the callable is proportional to the square of the request queue length, so a long-running callable may cause undesirable delays when the queue length grows.
It should return true if the requests can be merged, and False otherwise. For example:
@defer.inlineCallbacks def collapseRequests(master, builder, req1, req2): "any requests with the same branch can be merged" # get the buildsets for each buildrequest selfBuildset , otherBuildset = yield defer.gatherResults([ master.data.get(('buildsets', req1['buildsetid'])), master.data.get(('buildsets', req2['buildsetid'])) ]) selfSourcestamps = selfBuildset['sourcestamps'] otherSourcestamps = otherBuildset['sourcestamps'] if len(selfSourcestamps) != len(otherSourcestamps): defer.returnValue(False) for selfSourcestamp, otherSourcestamp in zip(selfSourcestamps, otherSourcestamps): if selfSourcestamp['branch'] != otherSourcestamp['branch']: defer.returnValue(False) defer.returnValue(True) c['collapseRequests'] = collapseRequests
In many cases, the details of the
sourcestamp and
buildrequest are important.
In the following example, only
buildrequest with the same “reason” are merged; thus developers forcing builds for different reasons will see distinct builds.
Note the use of the
buildrequest.BuildRequest.canBeCollapsed method to access the source stamp compatibility algorithm.
@defer.inlineCallbacks def collapseRequests(master, builder, req1, req2): canBeCollapsed = yield buildrequest.BuildRequest.canBeCollapsed(master, req1, req2) if canBeCollapsed and req1.reason == req2.reason: defer.returnValue(True) else: defer.returnValue(False) c['collapseRequests'] = collapseRequests
Another common example is to prevent collapsing of requests coming from a
Trigger step.
Trigger step can indeed be used in order to implement parallel testing of the same source.
Buildrequests will all have the same sourcestamp, but probably different properties, and shall not be collapsed.
Note
In most of the cases, just setting collapseRequests=False for triggered builders will do the trick.
In other cases,
parent_buildid from buildset can be used:
@defer.inlineCallbacks def collapseRequests(master, builder, req1, req2): canBeCollapsed = yield buildrequest.BuildRequest.canBeCollapsed(master, req1, req2) selfBuildset , otherBuildset = yield defer.gatherResults([ master.data.get(('buildsets', req1['buildsetid'])), master.data.get(('buildsets', req2['buildsetid'])) ]) if canBeCollapsed and selfBuildset['parent_buildid'] != None and otherBuildset['parent_buildid'] != None: defer.returnValue(True) else: defer.returnValue(False) c['collapseRequests'] = collapseRequests
If it’s necessary to perform some extended operation to determine whether two requests can be merged, then the
collapseRequests callable may return its result via Deferred.
Warning
Again, the number of invocations of the callable is proportional to the square of the request queue length, so a long-running callable may cause undesirable delays when the queue length grows.
For example:
@defer.inlineCallbacks def collapseRequests(master, builder, req1, req2): info1, info2 = yield defer.gatherResults([ getMergeInfo(req1), getMergeInfo(req2), ]) defer.returnValue(info1 == info2) c['collapseRequests'] = collapseRequests
2.7.3.
If the change frequency is higher than the turn-around of the builders, the following approach might be helpful:
def prioritizeBuilders(buildmaster, builders): """Prioritize builders. First, prioritize inactive builders. Second, consider the last time a job was completed (no job is infinite past). Third, consider the time the oldest request has been queued. This provides a simple round-robin scheme that works with collapsed builds.""" def isBuilding(b): return bool(b.building) or bool(b.old_building) builders.sort(key = lambda b: (isBuilding(b), b.getNewestCompleteTime(), b.getOldestRequestTime())) return builders c['prioritizeBuilders'] = prioritizeBuilders
2.7.4.
The
nextBuild function is passed as parameter to
BuilderConfig:
... BuilderConfig(..., nextBuild=nextBuild, ...) ...
2.7.5.
canStartBuild Functions¶
Sometimes, you cannot know in advance what workers to assign to a
BuilderConfig.
For example, you might need to check for the existence of a file on a worker before running a build on it.
It is possible to do that by setting the
canStartBuild callback.
Here is an example that checks if there is a
vm property set for the build request.
If it is set, it checks if a file named after it exists in the
/opt/vm folder.
If the file does not exist on the given worker, refuse to run the build to force the master to select another worker.
@defer.inlineCallbacks def canStartBuild(builder, wfb, request): vm = request.properties.get('vm', builder.config.properties.get('vm')) if vm: args = {'file': os.path.join('/opt/vm', vm)} cmd = RemoteCommand('stat', args, stdioLogName=None) cmd.worker = wfb.worker res = yield cmd.run(None, wfb.worker.conn, builder.name) if res.rc != 0: defer.returnValue(False) defer.returnValue(True)
You can extend this example using any remote command described in the Master-Worker API.
2.7.6. Customizing SVNPoller¶
Each source file that is tracked by a Subversion repository has a fully-qualified SVN URL in the following form:
(REPOURL)(PROJECT-plus-BRANCH)(FILEPATH).
When you create the
SVNPoller, you give it a
repourl.
2.7.6.1..plugins import changes c['change_source'] = changes.SVNPoller( repourl="")
repourl=
repourl=.plugins import changes, util c['change_source'] = changes.SVNPoller("svn://svn.twistedmatrix.com/svn/Twisted", split_file=util.svn.plugins import util def split_file_projects_branches(path): if not "/" in path: return None project, path = path.split("/", 1) f = util.svn.split_file_branches(path) if f: info = dict(project=project, path=f[1]) if f[0]: info['branch'] = f[0] return info return f
Again, this is provided by default. To use it you would do this:
from buildbot.plugins import changes, util c['change_source'] = changes.SVNPoller( repourl="", split_file=util.svn.
2.7.6.2..plugins import changes c['change_source'] = changes.SVNPoller("")
But what happens when we want to track multiple Nevow branches?
We have to point our
repourl=.plugins import changes c['change_source'] = changesreturn))
2.7.7..
2.7.7.1..
2.7.7.2. calls the
poll method according to the
pollInterval and
pollAtLaunch options.
The
poll method should return a Deferred to signal its completion.
Aside from the service methods, the other concerns in the previous section apply here, too.
2.7.8. Writing a New Latent Worker Implementation¶
Writing a new latent worker should only require subclassing
buildbot.worker.AbstractLatentWorker.worker.ec2.EC2LatentWorker for an example.
2.7.9.(...)
2.7.10. Factory Workdir Functions¶
Note
While factory workdir function is still supported, it is better to just use the fact that workdir is a renderables attribute of every steps.
A Renderable has access to much more contextual information, and also can return a deferred.
So you could say
build_factory.workdir = util.Interpolate("%(src:repository)s to achieve similar goal.
It is sometimes helpful to have a build’s workdir determined at runtime based on the parameters of the build.
To accomplish this, set the
workdir attribute of the build factory to a callable.
That callable will be invoked with the list_stamps): return hashlib.md5(source_stamps[0].repository).hexdigest()[:8] build_factory = factory.BuildFactory() build_factory.workdir = workdir build_factory.addStep(Git(mode="update")) # ... builders.append ({'name': 'mybuilder', 'workername': 'myworker', 'builddir': 'mybuilder', 'factory': build_factory})
The end result is a set of workdirs like
Repo1 => <worker-base>/mybuilder/a78890ba Repo2 => <worker.
2.7.11. Writing New BuildSteps¶
Warning
Buildbot has transitioned to a new, simpler style for writing custom steps. See New-Style Build Steps for details. This section documents new-style steps. Old-style steps are supported in Buildbot-0.9.0, but not in later releases..
2.7.11.1. Writing BuildStep Constructors¶
Build steps act as their own factories, so their constructors are a bit more complex than necessary.
The configuration file instantiates a
BuildStep object, but the step configuration must be re-used for multiple builds, so Buildbot needs some way to create more steps.
2.7.11.2..
2.7.11.3. Running Commands¶
To spawn a command in the worker, create a
RemoteCommand instance in your step’s
run method and run it with
runCommand:
cmd = RemoteCommand(args) d = self.runCommand(cmd)
The
CommandMixin class offers a simple interface to several common worker-side commands.
For the much more common task of running a shell command on the worker,)
2.7.11.4..
2.7.11.5..
2.7.11.6. Writing Log Files¶
Most commonly, logfiles come from commands run on the worker. worker to watch a actual file on disk.
The worker.
2.7.11.7..
2.7.11.8. Adding LogObservers¶
Most shell commands emit messages to stdout or stderr as they operate, especially if you ask them nicely with a option –verbose flag of some sort.
They may also write text to a log file while they run.
Your
BuildStep can watch this output as it arrives, to keep track of how much progress the command has made.plugins import util class TrialTestCaseCounter(util helps Buildbot to determine the ETA for the step..
2.7.11.9. Using Properties¶
In custom
BuildSteps, you can get and set the build properties with the
getProperty and
setProperty methods.
Each takes a string for the name of the property, and returns or accepts an arbitrary JSON-able (lists, dicts, strings, and numbers) step starts, so they cannot use the value of any properties determined in that step.
2.7.11.10.
getStatistic methods.
The
hasStatistic method determines whether a statistic exists.
The Build method
getSummaryStatistic can be used to aggregate over all steps in a Build.
2.7.11 file.)
2.7.11.12. Discovering files¶
When implementing a
BuildStep it may be necessary to know about files that are created during the build.
There are a few worker commands that can be used to find files on the worker and test for the existence (and type) of files and directories.
The worker provides the following file-discovery related commands:
- stat calls
os.statfor a file in the worker’s build directory. This can be used to check if a known file exists and whether it is a regular file, directory or symbolic link.
- listdir calls
os.listdirfor a directory on the worker. It can be used to obtain a list of files that are present in a directory on the worker.
- glob calls
glob.globon the worker,.plugins import steps, util from buildbot.interfaces import WorkerTooOldError import stat class MyBuildStep(steps.BuildStep): def __init__(self, dirname, **kwargs): buildstep.BuildStep.__init__(self, **kwargs) self.dirname = dirname def start(self): # make sure the worker knows about stat workerver = (self.workerVersion('stat'), self.workerVersion('glob')) if not all(workerver): raise WorkerToo(util.FAILURE) return s = cmd.updates["stat"][-1] if not stat.S_ISDIR(s[stat.ST_MODE]): self.step_status.setText(["'tis not a directory"]) self.finished(util.WARNINGS) return cmd = buildstep.RemoteCommand('glob', {'path':(util.FAILURE) return files = cmd.updates["files"][-1] if len(files): self.step_status.setText(["Found pycs"]+files) else: self.step_status.setText(["No pycs found"]) self.finished(util.SUCCESS)
For more information on the available commands, see Master-Worker API.
Todo
Step Progress BuildStepFailed
2.7.12. Writing Dashboards with Flask or Bottle¶
Buildbot Nine UI is written in Javascript. This allows it to be reactive and real time, but comes at a price of a fair complexity. Sometimes, you need a dashboard displaying your build results in your own manner but learning AngularJS for that is just too much.
There is a Buildbot plugin which allows to write a server side generated dashboard, and integrate it in the UI.
# This needs buildbot and buildbot_www >= 0.9.5 pip install buildbot_wsgi_dashboards flask
This plugin can use any WSGI compatible web framework, Flask is a very common one, Bottle is another popular option.
The application needs to implement a
/index.htmlroute, which will render the html code representing the dashboard.
The application framework runs in a thread outside of Twisted. No need to worry about Twisted and asynchronous code. You can use python-requests or any library from the python ecosystem to access other servers.
You could use HTTP in order to access Buildbot REST API, but you can also use the Data API, via the provided synchronous wrapper.
buildbot_api.dataGet(path, filters=None, fields=None, order=None, limit=None, offset=None):
This is a blocking wrapper to master.data.get as described in Data API. The available paths are described in the REST API, as well as the nature of return values depending on the kind of data that is fetched. Path can be either the REST path e.g.
"builders/2/builds/4"or tuple e.g.
("builders", 2, "builds", 4). The latter form being more convenient if some path parts are coming from variables. The Data API and REST API are functionally equivalent except:
buildbot_api.dataGetis accessible via the WSGI application object passed to
wsgi_dashboardsplugin (as per the example).
That html code output of the server runs inside AngularJS application.
- It will use the CSS of the AngularJS application (including the Bootstrap CSS base). You can use custom style-sheet with a standard
styletag within your html. Custom CSS will be shared with the whole Buildbot application once your dashboard is loaded. So you should make sure your custom CSS rules only apply to your dashboard (e.g. by having a specific class for your dashboard’s main div)
- It can use some of the AngularJS directives defined by Buildbot UI (currently only buildsummary is usable).
- It has full access to the application JS context.
Here is an example of code that you can use in your
master.cfg to create a simple dashboard:
from __future__ import absolute_import from __future__ import print_function import os import time import requests from flask import Flask from flask import render_template from buildbot.process.results import statusToString mydashboardapp = Flask('test', root_path=os.path.dirname(__file__)) # this allows to work on the template without having to restart Buildbot mydashboardapp.config['TEMPLATES_AUTO_RELOAD'] = True @mydashboardapp.route("/index.html") def main(): # This code fetches build data from the data api, and give it to the # template builders = mydashboardapp.buildbot_api.dataGet("/builders") builds = mydashboardapp.buildbot_api.dataGet("/builds", limit=20) # properties are actually not used in the template example, but this is # how you get more properties for build in builds: build['properties'] = mydashboardapp.buildbot_api.dataGet( ("builds", build['buildid'], "properties")) build['results_text'] = statusToString(build['results']) # Example on how to use requests to get some info from other web servers code_frequency_url = "" results = requests.get(code_frequency_url) while results.status_code == 202: # while github calculates statistics, it returns code 202. # this is no problem, we just sleep in our thread.. time.sleep(500) results = requests.get(code_frequency_url) # some post processing of the data from github graph_data = [] for i, data in enumerate(results.json()): graph_data.append( dict(x=data[0], y=data[1]) ) # mydashboard.html is a template inside the template directory return render_template('mydashboard.html', builders=builders, builds=builds, graph_data=graph_data) # Here we assume c['www']['plugins'] has already be created earlier. # Please see the web server documentation to understand how to configure # the other parts. c['www']['plugins']['wsgi_dashboards'] = [ # This is a list of dashboards, you can create several { 'name': 'mydashboard', # as used in URLs 'caption': 'My Dashboard', # Title displayed in the UI' 'app': mydashboardapp, # priority of the dashboard in the left menu (lower is higher in the # menu) 'order': 5, # available icon list can be found at 'icon': 'area-chart' } ]
Then you need a
templates/mydashboard.html file near your
master.cfg.
This template is a standard Jinja template which is the default templating engine of Flask.
<div class="container mydashboard"> <style> /* only modify th from this dashboard! */ .mydashboard table th { font-size 24pt; } </style> <!-- Create a table of builds organised by builders in columns --> <table class="table"> <tr> <!-- Generate the table header with name of builders --> {% for builder in builders %} <th> {{builder.name}} </th> {% endfor %} </tr> {% for build in builds %} <tr> {% for builder in builders %} <th> <!-- If this build is from this builderid, then we render it in this cell --> {% if build.builderid == builder.builderid %} <!-- for representing a build, you can choose one of those three forms --> <!-- 1) We use buildbot internal CSS styles display our builds, with links to the standard UI --> <a class="badge-status badge results_{{build.results_text | upper}}" href="#/builders/{{build.builderid}}/builds/{{build.number}}"> {{build.number}} </a> <!-- 2) The buildsummary directive is very powerful and will display steps, sub-builds, logs, urls. --> <buildsummary buildid="{{build.buildid}}" condensed="1"/> <!-- 3) If you need something lighter, there is the build sticker directive --> <buildsticker buildid="{{build.buildid}}"/> <!-- Note that those two directives will make additional HTTP requests from the browser in order to fetch the necessary data they need to be rendered. --> {% endif %} </th> {% endfor %} </tr> {% endfor %} </table> <!-- Example of line chart using Chart.js --> <canvas id="myChart" width="400" height="400"></canvas> <script> // We use Chart.js for rendering a chart, we first have to download it from internet // (will be cached by the browser) $.getScript("", // See for more details function createChart() { var scatterChart = new Chart("myChart", { type: 'line', data: { datasets: [{ label: 'Github statistics', // Here the data from the python is passed to the javascript via tojson and safe jinja filters // data: {{graph_data | tojson |safe }} }] }, options: { scales: { xAxes: [{ type: 'linear', position: 'bottom' }] } } }); }); </script> </div>
2.7.13. A Somewhat Whimsical Example (or “It’s now customized, how do I deploy it?”)¶ ‘framboozler’ command from the top of your source code tree. The ‘fram.plugins import steps, util class FNURRRGHCounter(util.LogLineObserver): numTests = 0 def outLineReceived(self, line): if "FNURRRGH!" in line: self.numTests += 1 self.step.setProgress('tests', self.numTests) class Framboozle(steps.ShellCommand): command = ["framboozler"] def __init__(self, **kwargs): steps number of different options:
2.7.13.1. Inclusion in the
master.cfg file¶
The simplest technique is to simply put the step class definitions in your
master.cfg file, somewhere before the
BuildFactory definition where you actually use it in a clause like:
f = BuildFactory() f.addStep(SVN(repourl=.
2.7.13.2.(repourl="stuff")) f.addStep(Framboozle())
or:
import framboozle f = BuildFactory() f.addStep(SVN(repourl="stuff")) f.addStep(framboozle.Framboozle()).
2.7.13.3. Install this code into a standard Python library directory¶.
2.7.13.4. Distribute a Buildbot Plug-In¶
First of all, you must prepare a Python package (if you do not know what that is, please check How to package Buildbot plugins, where you can find a couple of pointers to tutorials).
When you have a package, you will have a special file called
setup.py.
This file needs to be updated to include a pointer to your new step:
setup( ... entry_points = { ..., 'buildbot.steps': [ 'Framboozle = framboozle:Framboozle' ] }, ... )
Where:
buildbot.stepsis the kind of plugin you offer (more information about possible kinds you can find in How to package Buildbot plugins)
framboozle:Framboozleconsists of two parts:
framboozleis the name of the Python module where to look for
Framboozleclass, which implements the plugin
Framboozleis the name of the plugin.
This will allow users of your plugin to use it just like any other Buildbot plugins:
from buildbot.plugins import steps ... steps.Framboozle ...
Now you can upload it to PyPI where other people can download it from and use in their build systems. Once again, the information about how to prepare and upload a package to PyPI can be found in tutorials listed in How to package Buildbot plugins.
2.7.13.5. Submit the code for inclusion in the Buildbot distribution¶
Make a fork of buildbot on or post a patch in a bug at. In either case, post a note about your patch to the mailing list, so others can provide feedback and, eventually, commit it.
When it’s committed to the master, the usage is the same as in the previous approach:
from buildbot.plugins import steps, util ... f = util.BuildFactory() f.addStep(steps.SVN(repourl="stuff")) f.addStep(steps.
2.7.13.6. Summary¶. | https://docs.buildbot.net/1.1.2/manual/customization.html | CC-MAIN-2020-34 | refinedweb | 3,407 | 50.12 |
Feedback
Getting Started
Discussions
Site operation discussions
Recent Posts
(new topic)
Departments
Courses
Research Papers
Design Docs
Quotations
Genealogical Diagrams
Archives
Scheme has an IEEE standard, IEEE 1178-1990, which describes a version of the language slightly later than R4RS (#f and the empty list are definitely different) but not yet R5RS (no syntax-rules, dynamic-wind, or multiple values). That standard was reaffirmed unchanged in 2008, and will come up again for renewal in 2018. What's the Right Thing?
#f
I see three reasonable courses of action:
1) Do the work to make R7RS-small the new edition of IEEE Scheme.
2) Do the (lesser amount of) work to reaffirm IEEE Scheme unchanged for the second time.
3) Do nothing and allow the IEEE standard to expire.
Does anyone still care about having an official, citable standard for Scheme?
(When I brought the question up on #scheme, someone asked what R7RS-small implementations exist. Currently there are Chibi, Chicken (partial), Foment, Gauche, Guile (partial), Husk, Kawa, Larceny, Mosh (partial), Picrin, Sagittarius.)
I'm no longer a regular user of Scheme, I do not use the recent versions of it at all, and I'm no longer a member of IEEE. So I'm not going to spearhead the standard renewal process with IEEE again.
I also feel that recent language design choices have made the language less worthwhile to use, and wouldn't like the job of defending them to a committee.
Sadly, R4 may be the most recent step in the right direction that the language design took, and positive progress has ceased.
In particular, and starting with the worst misstep:
The handling of Unicode as specified since R6 is just plain wrong.
It makes people have to care how strings are represented and preserves a "character" data type which is representation-dependent and not a tenable primitive for expressing strings given Unicode string equality semantics. It breaks homoiconicity to have different rules for symbols and strings. And if you really need an array of codepoints, then it can only be because you are using it for something that is not a semantically sensible operation for strings. People want to treat strings as arrays of characters but in order to do that they have to have a "character" unit which no longer maps to anything human beings think of as characters and also randomly assigns different lengths to the same string when it happens to be expressed using different sequences of codepoints. Transformations that "patch up" these inconsistencies usually do so in ways that create further inconsistencies; they make it possible for example, to split strings and then concatenate the divided parts and get a different string than you started with.
It is an error to conflate arrays and strings given that string equality as understood by humans and as specified in Unicode is no longer dependent on the equality of array elements, and that string length as understood by humans and specified by Unicode no longer matches the number of array elements. Furthermore, manipulation of arrays of the codepoints which the standard is now mistaking for characters, requires Unicode standardized operations providing semantic operations on strings, to be re-implemented in scheme. Divisions on codepoint as opposed to character boundaries can create characters that were not there before and can create malformed strings that start with non-characters such as bare accents. Mistakes can easily result in other malformed sequences which are not strings, in strings which contain things that are not and never have been characters, and treatment of strings as a non-linguistic array of data encourages non-string misuse of the structure..
Something which is less bad, but still wrong:
Exceptions are a serious impedance mismatch for continuation-based control. And guard forms as specified by winding continuations since R5 are not compatible with exceptions at all. If you want exceptions, you need a multithreading mechanism that they do not conflict with. If you want continuation-based control you need continuation arguments to call in case of whatever event. If you want these to be dynamically scoped rather than explicit arguments, which most people who want continuations desire, then you need to nail down the semantics of a dynamically scoped environment for them to be variables within. Scheme already has dynamic scoping for certain constructs such as current-output-port and so on, and ought to have either scraped these out for consistency with lexical scoping, or nailed down semantics for its dynamic scoping, long ago.
Moving on to something not quite as bad but still wrong:
The handling of uniform numeric vectors as specified in R7 is also just plain wrong, for similar reasons to the reasons why strings are now wrong. It invites people to write code which relies for its correctness on limitations of the underlying data representation, and in which the same constructs have different semantics when applied to different objects which are nominally of the same type.
Finally, something that is a damn shame although not quite completely wrong:
Multiple returns are a good idea but the multi-argument continuations specified in R5 and subsequent standards make them hard to use, ridiculous, and confusing. They needed a proper syntax that allowed binding the return values to variable names at the call site and within a definite scope, in a way consistent with the way lambda expressions bind values to variable names at the definition site and within a definite scope.
In general, I consider many major design decisions since R4 to be mistakes. Most new constructions are not sufficiently well designed to be consistent. In many cases elements have been introduced which conflict with each other or with existing design elements. No one is attempting to preserve the semantic simplicity which derived from being able to think in terms of semantic types with uniform operations rather than in terms of machine representations with many different semantics for similar operations. That semantic complication is a rich source of program errors and lessens the utility of the language as a means of expressing, explaining, or reasoning about algorithms.
R4 was a limited language, but at least the parts it had were parts that actually fit together. What we have now, isn't worth the effort to make a standard for.
I'm no longer a regular user of Scheme, I do not use the recent versions of it at all, and I'm no longer a member of IEEE. So I'm not going to spearhead the standard renewal process with IEEE again.
I didn't expect it.
R4 may be the most recent step in the right direction that the language design took
You don't mention syntax-rules. Do you consider that a mistake as well?
syntax-rules.
I agree 110%. Unfortunately, it was simply not within the remit of the Working Group to make backward incompatible changes with IEEE 1178. Our charter set an unreasonably high bar against that. I'd love to see R8RS take exactly this view.
I would add one further point and one caveat. The use of non-negative integers to index into strings is a mistake: string cursors should be opaque objects. SRFI 130 (a rewrite of Olin's SRFI 13 string library) takes this point of view. The caveat is that you assume that there is a single point of view about what constitutes a character to a human being, but that turns out not to be the case: people can and do disagree about how to divide the same text into characters. That being so, the codepoint view provides a rock-bottom mechanism that other more sophisticated views can be layered on in order to serve different purposes.
Scheme already has dynamic scoping for certain constructs such as current-output-port and so on, and ought to have either scraped these out for consistency with lexical scoping, or nailed down semantics for its dynamic scoping, long ago.
Formal semantics is all Greek to me, so I can't defend this point, but I've been told that the R7RS formal semantics does nail this down.
The handling of uniform numeric vectors as specified in R7 is also just plain wrong
I don't understand your reasoning here. It's true that you can't do anything with bytevectors that cannot already be done with vectors, but you cannot do anything with vectors that cannot be done with lists. Indeed, a vector can be abstractly considered as a list of pairs whose cars are mutable and whose cdrs are immutable.
Multiple returns are a good idea but [...] needed a proper syntax that allowed binding the return values to variable names at the call site and within a definite scope, in a way consistent with the way lambda expressions bind values to variable names at the definition site and within a definite scope.
The R7RS syntax let-values, let*-values, and define-values serve this purpose, if I understand your objection correctly. The first two come from SRFI 11 and are present in R6RS as well.
let-values
let*-values
define-values
"You don't mention syntax-rules. Do you consider that a mistake as well?"
I do.
I'd be much happier with a more powerful system that wasn't a dsl.
I made comments about it here and here
I'm conflicted about syntax-rules. On the one hand, it enables some things that truly needed to be enabled - hygiene is a somewhat serious restriction when a language has no access to any dynamically scoped structures. As reflected by the fact that more than half of Scheme's native syntax forms deal with its special predefined set of dynamic variables.
On the other hand, what was needed to serve that role was a proper semantics for dynamically scoped variables that didn't allow them to be confused with or shadowed by lexically scoped variables. That would have made all sensible usage of syntax-rules unnecessary, and the particular semantics they chose is unclear, inconsistent with the rest of the language, and can be used to provoke completely unexpected behavior such as hiding a function evaluation within the evaluation of a symbol which appears to be merely a variable reference.
So I'm categorizing syntax-rules under "the surgeon really did need a cutting instrument; a scalpel probably would have been more appropriate than a chain saw."
Can you give an example of a system of macros with dynamically scoped variables that solves the hygiene problem? I say that because I really don't understand and I want to since I'm about to be implementing a macro system.
would like to hear this point expanded upon. Seems to me the part about not confusing dynamic variables with static ones is rather key. How to you distinguish them? A symbol is a symbol... unless you use some convention to distinguish, like the way classic BASIC suffixed $ on a variable name to denote a string. (Of course, Kernel coped with hygiene using first-class environments, which, whatsoever its merits or demerits, is quite a radical solution and is surely one of the reasons Kernel is, as remarked elsewhere in this thread, not a Scheme.)
In ISLisp there are special forms defdynamic to create a globally scoped dynamic variable, dynamic-let to bind one or more of them, dynamic to fetch its value, and setf with dynamic to assign it. So essentially they are in a distinct namespace, as function names are in ISLisp and Common Lisp.
defdynamic
dynamic-let
dynamic
setf
I used 'with' in pretty much exactly the same way as 'let' to create dynamically scoped variables, and had them occupy a separate name space (dynamic variable names must start and end with asterisks and have at least one character between them, and non-dynamic variable names are not allowed to do both).
I understand that a Unicode codepoint isn't a character, but what's wrong with defining "character" along the lines you just sketched and taking a "string" to be a list of those? I assume there is a uniqueness property for Unicode (i.e. if ABC can be split into AB and C and also into A and BC, then it can be split into A, B, C). That's true, isn't it?
Not all scripts have as well-defined a notion of characters as Latin or Han. For example, there are three human-oriented ways to view Devanagari text: (1) the phonemic level, where letters (consonants and initial vowels) and vowel signs are separate units; (2) the default grapheme cluster level, where a letter with or without a vowel sign is the unit; (3) the akshara level, where a (possibly zero-length) sequence of graphically reduced letters followed by a fully written letter followed by an optional vowel sign or virama (vowel suppressor) is the unit. None of these is inherently superior to any other, and what people see as "a character" depends on their purpose at the time. Furthermore, none of these three levels is equivalent to the codepoint level, but all of them can be constructed on top of it.
Even the familiar Latin script is not so simple as it seems. In English æ is a mere typographical ligature, and it is all one whether you write Caesar or Cæsar, but in Norwegian æ is a separate letter, not interchangeable with ae. By the same token, sœur is the normative French spelling of the word for 'sister', but it is commonplace to write soeur nowadays because œ got squeezed out of the Latin-1 character set; however, moelle 'marrow' cannot be spelled mœlle (it is pronounced as if written moile). In German and French respectively, ä and é require their accents, but don't constitute separate letters of the alphabet, whereas in Swedish and Icelandic they are as separate as i and j are in English (but not in Italian); English ö in coöperate is a typographical nicety used by The New Yorker but hardly anyone else nowadays.
This wouldn't stop me treating code points as 'Latin characters.' Of course, you're right there will be lots of languages where that should be called a misnomer. But for lots of applications, it should be sufficient to treat a Unicode string as an opaque piece of text only used for storing, comparing, and rendering.
I'm arguing against the claim that there are uniquely defined natural objects called "characters" such that a string is a sequence of them. It doesn't sound to me like you disagree with that.
I think of it mostly in terms of whether operations that are supposed to be well-defined can create malformed-ness and/or nonsense. I accept 'œ' as a character, for example, because if you subdivide it into strings containing 'o' and 'e', then concatenate those strings, you get 'oe' not 'œ'. So 'sœur' and 'soeur' are alternate spellings of the same word as far as I'm concerned, not different ways of writing the same spelling. Some languages have rules that permit certain alternate spellings to be constructed, and that's okay. But if the string changed as a result of a pair of operations that are supposed to be inverses, then the operations are not inverses, and that is not okay. The emergence of nonsense when you divide and rejoin means œ, and other ligatures, should be treated as indivisible.
Likewise I accept ä and é as characters, for similar reasons; if you subdivide them, you get a letter on one side of the division, and a bare accent on the other. Because a bare accent is not a character by itself, you have produced a malformed string. A malformed string means the division operation was an error, and therefore string division should not have operated at that boundary. And anyway ä and é exist in multiple versions in unicode; whether they're one codepoint or two is ambiguous, and the only way to sensibly resolve the ambiguity is to be counting grapheme clusters instead of codepoints.
There is another, IMO even stronger, reason why ä and é should not be subdivided; It is purely an accident of encoding that we're putting the codepoints for accents after the codepoints for the letters accented (Before the letter would actually have made more sense, if thinking in terms of designing electromechanical printers). If an arbitrary representation choice affects what you get as a result of an operation, then the operation is non-semantic, and your programming language is no longer working at the semantic level. In a machine-oriented language like C that's expected and appropriate, but C is for describing machine operations and Scheme is for describing semantic operations. The principle of least surprise cuts the other way.
Most string operations aren't meaningful. One of the most important string operations in practice is substitution / interpolation, but that's already difficult to get right. In English you have 'a' vs. 'an', plurals and number agreement, gender agreement, etc.
Strings as a list of characters seems like a useful abstraction to me. You may need new code to handle unusual cases, just like you need code to handle the edge cases of English in interpolation.
I would consider an o with an umlaut to be a single character.
String operations by themselves are mostly not meaningful, but they should be operations that would make sense to non-programmers working with text, and must also obey axioms that programmers can exploit. Doing both harmoniously is the crux of the design effort.
For example the axioms I invoked above about string division not creating malformed strings, and about string division and string concatenation being inverse operations of each other. Those are axioms a programmer can use and exploit, and they are also in harmony with the way people working with language think of writing it. The only reason why a non-programmer wouldn't understand those axioms is because the non-programmer would never have even considered the possibility of an operation that fails to obey them.
You're absolutely right that substitution/interpolation is one of the most important string operations. To be most useful to programmers, it has axioms it must follow. At a minimum it must create no malformed strings. And I would consider it broken if any substitution of an X for a Y could not be undone directly by a substitution of a Y for an X. When you start splitting on codepoint boundaries instead of character boundaries, those axioms break on one point or the other.
I don't have a problem with programmers having to worry about the idiosyncrasies of individual languages, but for a language that's describing things at a higher abstraction than machine operations I'm going to be really obstinate about programmers being able to use the same units of representation and the same semantic operations that the people writing the language with other tools use.
If a scholar with a brush and an ink stone doesn't have to think in terms of code points, then to the extent possible, neither should the programmer have to think in terms of code points. The reason it's okay that the programmer has to be the one who worries about the rules of individual languages is because the programmer is now in the place of that scholar, and in order to function the programmer, like that scholar, has to know the rules of his language's orthography. As language implementers we're providing the brush and the ink stone.
We should be thinking in terms of the operations the scholar uses. "Put an accent over that character" or "Use a different word" are operations that make sense in terms of what the scholar does, and they're operations we must provide. But the brush and the ink aren't the part of the system that has to know the linguistic rules about how to form plurals and make noun/verb agreement work. That's what language scholars who are the ones using the tools do.
It's easy to say that about ö. But what about Devanagari क्न्य knya? At the akshara level, it's a unitary character. At the default grapheme level it's three characters क् k + न् n + य ya. At the letter level it's क ka + ् vowel killer + न na + ् again plus य ya. Visually, the क gets reduced to just its left half and the न to a squiggle. You type at the letter level, so when you hit backspace, the rightmost letter disappears. But when you navigate through the text using the arrow keys or the mouse, you can't select in the middle of an akshara: when the character appears as क्न्य, it is just one letter; when it appears in the equivalent (but less legible) way as क्न्य, it is three.
All we can do is provide primitive operations that behave in a consistent manner and don't produce malformed strings. It is certain that subdividing must not separate the vowel killer from the truncated-syllable that would otherwise have the vowel. It is also certain that 'adding a symbol to an akshara' is an operation the people using the language actually do, in the same way we do 'adding an accent to a letter,' so it isn't unnatural to them to enter it as multiple operations the same way we enter letters.
As for the silly question of whether it's one or three, I'm sure that people actually using the language are able to decide for themselves when they want to use which kind of count. If they write it, as you suggest, in visually different styles intending different numbers of characters, then it is within their paradigm to understand that a thing can be 'spelled' in more than one way because they are the ones making the distinction.
If they don't want to *say* that it's a different spelling, that's fine; it's as consistent as an English-literate person insisting that 'œ' is the same spelling as 'oe.' It is true within the rules of their language but if they see and use the distinction, they can see the difference, and they can treat it differently when appropriate.
Anything which cannot be decided at the level of tools has to be decided at the level of actual use.
For at least the Indic languages Unicode is the way to go. Unicode's code points canonicalizes things very well. For example, the first "akshar" of my name in Gujarati would be written as બ and while one can say is it is composed of "half-letter" બ્ and vowel-sign ા, normally you wouldn't write it as two separate symbols. Nor would you write it in it true half-letter form (by omitting the vowel sign) except when it is immediately followed by consonant and even there the written form can vary depending on actual sounds. So for example "pr" would be written as પ્ર while "pl" would be written as પ્લ.
All this is now handled in how you present text via the font machinery. Internally, unicode codepoints regularize things quite a bit. Until Unicode the situation was quite a mess (almost always the encoding stored in a file was just whatever mapping provided by the particular font being used -- forget writing a common set of simple tools to work over all sorts of documents!).
If Scheme is to be used for Indic language processing unicode is pretty much required.
I very much like the model provided by Go (and in fact I first used Go to translate documents using font specific encodings to unicode). In Go a string is a UTF8 byte string. If you index or extract a substring using an index, you get a UTF8 "character" but if you range over a string with a "for loop", you get a sequence of unicode code points (they call them runes). Something similar would work well in Scheme. E.g. string-for-each and string-map. And may be a string-next-rune function. Then you can stop worrying about whether the underlying scheme used is UTF8 or something else. You still need string-ref and string-set! for building friendlier abtractions (such as regular expressions etc.).
I will agree that the codepoint representation provided by Unicode is a far better representation for pretty much all languages that have writing systems more complicated than ASCII can serve. Which is essentially all of them. Including English. Even for English-language writing in a presumed context of one country, ASCII was a harshly minimalistic judgment call about which things to leave out.
Any system which represents language well enough, was going to break that one-codepoint-per-printing-character assumption that programmers used to rely on, because that assumption is pretty much wrong. A lot of languages have open-ended construction rules - Even in the Latin alphabet that we're using here, there is no real limit (aside from practicality) on how many accents and diacritics are valid. Heck, I've seen mathematics use A-prime, A-Double-prime, A-Triple-prime, etc... There's not even a limit just in repetitions of the same diacritic, and we were going to have to get that.
Unicode is badly designed for a completely different reason. Well, a bunch of them actually, but only one that's truly unforgivable. It allows different sequences of values to be representations of the same string.
If two strings are identical I don't want to be able to detect any difference between them. I don't want it to matter what operations I did to get them. I don't want them to break apart differently. I don't want joining them to something to give different results. I don't want the same character location in identical strings to be indexed by different numbers. There is absolutely no way to deal with that except by abstracting string handling above the level of codepoints.
That implies eager normalization for strings - where absolutely every string and character is in the same normalization form, where there is no operation on strings that can yield a denormalized string, and where it doesn't even matter what normalization form that happens to be - where different implementations can use different normalization forms under the hood and software operating on the same strings will yield the same results.
Among other things that means a bunch of stuff we are accustomed to using strings for - essentially every usage where the string is used as anything other than a sequence of HUMAN LANGUAGE - needs to be expressed as operations on arrays instead.
And that includes handling sequences of codepoints, if we're handling them in any context other than as constituents in human language. A sequence of codepoints can be non-normalized, or can contain partial characters, or other things that make nonsense when considered in terms of human language, and if we allow strings to do those things we break every programming axiom in the world as regards string identity and consistency of operations.
That implies eager normalization for strings
The kind of character and string types you advocate for are agnostic as to normalization because they abstract it away. The question doesn't arise.
At the codepoint level and below, the option not to eagerly normalize is vital for practical reasons.
At the codepoint level and below, the option to not eagerly normalize, yes, is vital for practical reasons.
That's exactly why people must not be forced to work with strings at the codepoint level and below. At that level they are no longer strings.
What I mean by eager normalization was that if the programmer CARES about what normalization form the implementation uses to store strings, it means string identity semantics have failed. If the goal is that all instances of a particular string value must have the same semantics, then eager normalization (forcing all instances of that value to have the same representation) is the simplest way of achieving it.
The sole exception - the ONLY place codepoints ought to rise to the level of programmer attention - is when they are unavoidable. There are essentially two places where that happens. The first is when the codepoint is being used as an integer for some non-linguistic purpose such as indexing into a table or structure. In that case you're not using a character, you're using a numeric value cast from a character.
The second is binary I/O. Binary I/O ports, by definition, aren't reading and sending strings from and to the outside world, they're reading and sending blobs. If you send a string through a binary I/O port then the port will have to cast it to blob before it can send it.
Because there are several normalization forms and endiannesses, the i/o ports need to be able to make any of several different casts to do that. So it's reasonable that the programmer should be concerned with (able to specify) which casts a port will use to create or translate its blobs.
If you are using codepoint values in some way that allows the creation of or requires the interpretation of denormalized sequences then you are not using them as characters. If you ask a binary port for a blob, or ask it to write a blob, it will happily do that with no casts to or from strings - reading and writing blobs, after all, is what it's for. If you want to manipulate that sequence as a sequence of binary in uniform widths, that's fine too; that's what array operations are for.
But when you cast any blob value to a string, you get the same string value (or the same error, if it contains a non-codepoint or invalid sequence). When you cast any string value to a blob, you get the same blob value. Unfortunately blobs have a many-to-one relation to both strings and errors, so the conversion is lossy in one direction.
I tend to write answers that are too long.
In more direct and appropriate response to your point:
At the codepoint level and below, the option not to eagerly normalize is vital for practical reasons.
What you are talking about here is the sort of non-linguistic operations that we have been mistaking for string operations, but which are not. I do not deny the need for operations on arrays of binary values. I have no problem with the idea that binary values can be cast to and from characters and strings according to their values as codepoints. I have no problem with cast operations that can convert between arrays of integers and strings. But the array of binary values cannot be a string any longer, because the conversion from arrays of binary to strings is lossy; many arrays of binary cannot be made into strings, and many different arrays of binary can be made into the same string.
"Unicode is badly designed for a completely different reason."
That may be but there is no other decent alternative at present if you want to work on some non-ascii text. If you live in an ascii only world, UTF8 encoding will work just fine for you! That is, we still need string-ref, string-set! but for "proper" unicode handling we will need more advanced functions (which in turn may use string-ref, string-set!, substring etc.). In other words decent Unicode support +UTF8 will end up being a pure superset of ASCII only world (and a "small subset" Scheme can simply ignore Unicode!).
"If two strings are identical I don't want to be able to detect any difference between them."
This is a low level boring sort of difference that can be easily handled at a different level (or in a preprocessing phase or something). Base unicode library functions can assume some normalized representation. Or you just write a (normalize ...) function if the input is too grotty. When I was looking at Gujarati spell checking, "same but different" is not where I spent my time. The interesting stuff was figuring out complex but well defined combining rules (see sandhi) and the kind of mistakes people might make. For that working at the codepoint level was just about ideal. My guess is Scheme would be a very good programming language choice for all sorts of natural language processing.
(normalize ...)
There are standard "normalize" procedures.
If you have one, and libraries do, you can always compare strings.
As an aside, your choice of title confuses me. Examining a hard case to make law ... isn't that what you're doing?
I see what you're saying that using a Character abstraction makes assumptions that don't hold in every use case for Unicode. I think that's a good argument that Character shouldn't be how Unicode is exposed. I'm not sure that it proves that the Character abstraction shouldn't exist. I'll have to think about it more. Thanks for the discussion.
I don't know what scheme proposes to do with unicode, but you just have to live with the fact that human languages are messy and have ligatures and you can't always fit a grapheme in any given number of bytes. In short, there's no way around the fact that programmers have to up their game to deal with Unicode and you need libraries that deal with the cases.
I'd be happy with:
1) utf8 - that leaves ascii as ascii and it's short
or
2) 32 bit "characters"
or
3) graphemes (no one does this, but scheme has bigints, so it's within the style of the language).
In any case you need a library that converts unicode to canonical form so that strings that render the same can be compared as the same.
The standard defines how to do that, and I've worked on libraries that do that. It takes a big table and some code, but that's life in the big wide world of supporting every language.
There's a passage in the introduction to the Scheme reports, starting with the R3RS, often quoted because it neatly captures an idea lots of people agree with (although they sometimes have aggressively incompatible notions of its practical implications):
Programming languages should be designed not by piling feature on top of feature, but by removing the weaknesses and restrictions that make additional features appear necessary.
I figure Scheme abrogated its claim on that philosophy when they added macros, dynamic-wind, and multiple-value returns. I've mused occasionally that the addition of macros might be dubbed the "second-class perversion" (alluding to Vernor Vinge's A Fire Upon the Deep). I presented alternatives to all three (mis)features in Kernel: first-class operatives instead of macros, guarded continuations instead of dynamic-wind, and generalized definiends instead of multiple-value returns. (It suddenly occurs to me I've never blogged about why I consider multiple-value returns wrong-headed, though it's discussed in a couple of places in the R-1RK, listed there in the index under "multiple-value returns". Key points are that $define! uses a generalized definiend — no discontinuous syntactic sugar for defining procedures — and that apply-continuation passes the argument tree to the continuation rather than merely passing the first argument as in Scheme.)
$define!
apply-continuation
That IMO much-overquoted remark has never applied to library features. If it did, R2RS (the first Scheme report to have a procedure library at all) would have had only car, cdr, cons, pair?, and null?, since lists and atoms (defined by exclusion) are a sufficient basis for programming anything, and there would have been no need for R[3-7]RS at all. (It actually suffices to allow just one atom.)
car
cdr
cons
pair?
null?
As you know, I admire Kernel very much, but it is not Scheme, and my purpose at present is determine how to standardize Scheme.
Doesn't apply to library features; quite right. Though none of those three issues is about library features. (Admittedly apply-continuation is library, but I merely used it as a more direct illustration of my point than the primitive continuation->applicative under which the relevant rationale discussion occurs.) Also granted, Kernel is a bit too far afield in design space to qualify as a Scheme; but I do maintain that those three features added to R5RS Scheme are philosophically inappropriate for Scheme because they introduce lack-of-generality into the language whereas there are ways to accomplish such things that are philosophically consistent as the R5RS solutions are not.
continuation->applicative
Scheme has always had second-class mutable variables rather than first-class boxes (cells). It's somewhat mysterious why this is so. Steele remarks somewhere that Scheme doesn't have cells because it would have taken an extra year to make it have them, and I always wondered what he meant by it. Certainly boxes (in the form of hunks) were available on Maclisp, and it would have simplified the Rabbit compiler considerably if all variables were immutable. I finally realized that he meant it would have taken too long to figure out how to optimize away the use of explicit boxes in cases where they were not necessary.
As dynamic languages go, Scheme is actually rather static in everything but its type system. For example, the effects of redefining a name in the global scope are undefined. Procedures are not S-expressions, though their external representations are.
I find this confusing.
When you say variables are second class instead of boxes I understand that as "you can't take a reference to a variable".
But then you say you want them to be immutable.
What's the point of immutable boxes? If they're immutable you might as well pass values.
A lot of languages can't pass by reference. It turns out not be a big deal, since you can box by hand in the very few cases that you need it.
Assignment conversion changes variables that are actually mutated (lexical scoping makes it possible to determine these for sure) into immutable variables holding mutable boxes, thus putting all mutation into data structures rather than the language itself. Some Scheme compilers in fact do this, on the assumption that mutating variables are rare and a few such boxes scattered through the heap is no big deal.
However, if you were to get rid of set! and simply require users to use the boxes themselves, as ML does, it becomes much harder to optimize away boxes when they turn out not to be necessary. It is precisely the advantage of making things second-class that they are often easier to optimize.
set!
Procedures are not S-expressions, though their external representations are.
I find myself uncertain what you mean by this statement. It might be a statement that procedures are encapsulated atomic objects (which is also true of Kernel operatives, and has nothing to do with static-versus-dynamic); or a statement that the standard does not require procedure objects to be evaluable (which would imply that they aren't first-class, and would honestly surprise me); or some other statement that I'm failing to imagine as a possibility.
Procedures as encapsulated objects were introduced into the Lisp tradition by Scheme. Before that, and right up to CLtL1 and Elisp, lists of the appropriate form are procedures, though perhaps not the only type of procedure. You could cons up a list whose car was lambda and pass it directly to apply. That's not possible (portably) in CLtL2 or ANSI Common Lisp, and has never been possible (portably) in Scheme. All code objects are knowable in advance (hence static), and the only thing that can be freely created at runtime is a closure with dynamically determined values of the closed-over variables and a known code object.
lambda
apply
The exception, of course, is a procedure created by eval. But eval did not exist in Scheme until R5RS, evaluates its first argument in an empty lexical scope, and there is no guarantee that the global scope in which the call to eval is executed is reified in such a way that it can be passed to eval at all. In principle, eval could invoke an entirely separate Scheme implementation that shares nothing with the calling program.
eval
Procedures as encapsulated objects were introduced into the Lisp tradition by Scheme.
The Art of the Interpreter views the pre-Scheme strategy as lacking first-class procedures, rather supporting only first-class representations of procedures. These are of course just different ways of saying the same thing, but I think I agree with Steele and Sussman that it's more useful to think of the earlier approach as not giving first-class status to procedure values. Procedures in this sense cannot be represented in source code — they are purely runtime entities, which is also why they are exempt from Wand's "theory of fexprs is trivial" effect (that is, Wand means by "theory" the theory of source expressions, and Lisp has a trivial theory of source expressions because all Lisp source expressions are passive data; procedures, being not source expressions, do not appear at all in Wand's trivial theory). Encapsulation of procedures is important for proving things about programs, but this is true regardless of whether the proofs apply to compile-time or runtime.
R5RS provides what I'd call a fake eval, since what makes eval a meaningful operation is first-class environments.
See my comment on conlanging and fossil faking to your most recent blog post. "Disjoint" might be less contentious.
compared with say, an eval in the current environment, if safer.
Mm. Evaluating in the current environment can be dangerous too if it's easy to overlook the dependency, which is why Kernel's eval always requires an explicitly specified environment argument. ("Dangerous things should be difficult to do by accident. :-) Personally I think eval really only comes into its own when it synergizes with lexical procedures capable of optionally capturing their dynamic environments.
Yes, "fake" is a rather harsh word choice. But I think it applies: not merely "not real" (similarly to the way conlangs are not real), but not real while misleadingly claiming to be real. It doesn't require deliberate deception, although to produce such a thing without deliberate deception would seem to involve some failure to recognize the lack of efficacy in what was adopted. Possibly the puzzling outwardly visible result of some compromise with a convoluted internal story.
See the other comment some thoughts on steering scheme.
Fake eval arises from a general pattern of shunning any dynamic, reflective features that are simple and easy in an on-the-fly graph-based interpreter, but that can be used in ways that thwart optimizing compilation.
In the early history of Scheme it was widely recognized that Scheme made sense and had a potentially bright future in both dynamic and static forms, and that the two forms could be harmonized. (Aubrey Jaffer's SCM and his original CHEAPY compiler (later replaced by Hobbit) sketch and provide evidence of this understanding.
Around the time of R4RS and then increasingly after, the authorities in control of the reports became hostile to the dynamic path. Leadership was dominated by the opinions of a few developers of academic research compilers.
Now that we have just in time, and even tracing compilers (even in some scheme implementations like Racket) the research should be into combining the two.
Racket still shows problems from that fight though.
Uh..no, that's several confusions combined.
1. JIT was well known and convincingly practiced no later than 1987, published by 1990 (Self). R4RS arrived in 1991.
2. Really, JIT in the context of graph-based lisp interpreters was understood no later than 1990 (SCM).
3. The dynamic, reflective features under consideration here are interesting in no small part because they can be usefully applied in ways that defy even JIT compilation.
The attitude that an interpreter has to be justified by an imagined potential to use any technology, even JIT, to compete with optimizing compilers of static code -- that attitude -- is what help the Scheme steerers drive away implementers like Jaffer (and me) and helped them lead the Scheme reports in the direction of being about the tastes of a very small number of compiler maintainers.
They treated Scheme standards as if they had to be protected like Cobol or Fortran standards; as if there were millions and millions of users more dependent on stability than advance.
Like Jefferson Airplane said: "Soon, you'll achieve the stability you strive for / in the only way it's granted / in a place someone puts fossils of our time."
Then I am using the wrong name but the thing I'm talking about was Jaffer's not Steele.
Jaffer had a little hack that would compile a tiny ad hoc subset of Scheme to simple-minded C to compile together with SCM. When Hobbit came along, it was a greatly cleaned up idea of the same concept.
I had the impression Jaffer's hack was for the purpose of some specific "day jobs" he was up to.
Without first-class mutable environments there is no way to use eval to accomplish anything that would justify its use in the first place. In pursuit of static optimizability, "eval" was effectively sacrificed; the only reason it remained in the language was to pay lip service to the tradition in which it had actually been useful.
It is well understood that 'eval' is hostile to static compilation, and that if you use it you will pay a heavy price. But that was not an adequate reason to blunt it into oblivion.
It is well understood that 'eval' is hostile to static compilation
Right. That's the problem I am running into. I am trying to make, not a Lisp, but a compiler for an untyped combinator language (with quotation) where most of the compiler internals are exposed to language such that it should be feasible to implement DSLs more easily.
But yeah. The problem sucks, I am not sure where to progress, and I am not sure I would end up with something worthwhile.
With Lisp, most of the low-hanging fruit regarding dynamic compilation seems to be eaten.
Isn't the problem with "eval" equivalent to module loading? You could compile the code in the eval to a shared object with unknown symbol bindings, and then let the dynamic linker resolve the environment. You would effectively build the code inside the eval as a .so or DLL and then pass the environment as a native symbol table to the dynamic library loader. That's probably as good as you can get statically, and would allow all static optimisations except inlining, which based on the fact you want to dynamically change symbol bindings is the best you could ever get statically.
I am not exactly sure what you are proposing but it doesn't feel like the right direction.
I have dumbed it down to two competing requirements:
1. I want to be able to write arbitrary functions over the AST resulting in new ASTs directly in the language. (If I could get rid of quotation that would be even better, I guess.)
2. It should be efficient. (And it should work in a REPL, of course.)
So, something like it should be able to pick up an expression, compile it, run it, and then continue with the next expression?
Isn't the aim to statically compile what is inside the eval, deferring calls mapped to the environment (and values by reference so they are mutable) until runtime? This is exactly what the dynamic link loader does when loading shared objects. It sounds like this is a valid solution to me, is it just that you don't like it, or want to do something more just-in-time?
The thing is I don't see any difficulty with JIT compiling the eval contents? You might want an intermediate byte code representation though, so you are not string parsing at runtime, but this seems like normal JIT compiling, so I thought you must want something else?
what's in the eval might be
(set! TopLevelFunctionThatsCalledEverywhere (lambda() (print "oh my god I changed the program")))
Either forcing the compiler to never inline functions or forcing it to pause and deoptimize running code (like Self used to).
As I commented elsewhere I don't think changing bindings for functions that are currently on the call stack is a good idea. What I wanted to allow was changing the bindings for the code in the eval, so you could call code with a different environment.
If you can pull the rug from code already in the call stack you would have to JIT compile, and set watches on symbols used in the call stack to invalidate the compile cache for that function, or indirect every call through a function table, still that would be no worse than virtual functions for performance.
The problem isn't TopLevelFunctionThatsCalledEverywhere is currently running. No, not at all.
The problem is that functions might have inlined TopLevelFunctionThatsCalledEverywhere, and that inline is now an invalid optimization. Those functions all have to be recompiled based on their optimization being wrong:
1) And some of THOSE functions might be running.
2) Worse than anything, imagine a loop that calls TopLevelFunctionThatsCalledEverywhere
a) and TopLevelFunctionThatsCalledEverywhere is inlined
b) and in this case it IS running
c) there is no call stack for it
d) you have to deoptimize the running program, CHANGE the call stack to simulate the function being on the call stack, deal with the impossible problem of how that function folded with outer code (I bet Self simply disabled most optimizations in the first place). And set it up so that the NEXT iteration gets the new function.
Think of how hard that is. E
A compiler is merely an optimisation, so "all" you need to do is preserve the behaviour you'd get if it was interpreted.
All you're changing is a binding; anything that already *has* that binding gets to keep it "as is", anything that uses the binding after it's been rebound gets the new version. Sure, dealing with inlined code is a bit tricksy, but I can think of a few ways of doing that which should only affect performance in the case where you *have* rebound stuff, and anyway, optimisation is hard.
The only hard stuff is if you actually *want* to rebind everything up the call stack. Perhaps I lack imagination, but I can't actually think of any case where you'd really want to do that.
The problem I am looking at is more general. One of the problems I encountered, for instance, is: If you quote something with the explicit intention of doing a source-to-source translation and compile it then how often are you going to compile? Once, for every compile instruction, or every time you encounter it in the body of an expression? Moreover, do you want to quote the source code or a runtime expression?
If you go the way of code-is-data there are lots of design decisions you can make beyond adopting the manner in which Lisp does it.
I saw this from time to time in scheme code. I think it came up most egregiously, in fact, in most of the early "records" implementations.
Somebody would want a user-definable type such as records, and they would implement it in terms of vectors, and then they would redefine vector-ref and vector-set so that those functions did not work on their brand new records.
And then of course that code would have a big ol' fight with someone else's code who had had the same idea, or with someone else's code whose continuations didn't catch at the point they were relying on having caught, or with someone else's winding continuations that were trying to protect references to particular other vectors with guard clauses, or ....
And that was about the point at which my hobby lisp started acquiring sigils that limited certain kinds of dynamism.
For one, I want to be able to have access to all ASTs. So, while compiling a quoted expression, where a symbol refers to a defined object, I want to be able to substitute its definition.
A bit uncommon but should allow one to build, for instance, computer algebra systems. (Although Mathematica would arguably be better at that.)
I am not sure about it. Weighing the pro's and cons' of various approaches.
That doesn't seem that odd, although different from what I was thinking. You just need a data structure that can represent code. This would not be a byte code but as you say an AST, with a binary in memory representation. It doesn't seem that different from an ordinary algebraic datatype. You would have a front end parser that converts everything to the AST format, then you could self modify the code. You would then JIT compile and invalidate the JIT cache if a functions source AST is modified.
Well. it turns out to be a hard problem (to get right.)
As long as the first-class environments can be iterated over, those are interdefinable. That said, I see R5RS and Kernel don't allow environments to be iterated over, so that might be a moot point.
I'll describe what I'm talking about anyway. Suppose our environments were association lists. We would like to write this:
(eval-in-env '(/ (+ b c) a)
(list (cons '/ /)
(cons '+ +)
(cons 'a 1)
(cons 'b 2)
(cons 'c 3)))
We can achieve the same thing with this:
( (eval-in-empty-env
'(lambda (/ + a b c)
(/ (+ b c) a)))
/ + 1 2 3)
We can define eval-in-env as a procedure that does this.
eval-in-env
If we don't like having the ability to iterate over environments (and I don't, necessarily), then I think we can proceed to write a library where these assoc lists are wrapped up in an encapsulated data type.
Your first version can easily be written in R5RS or earlier, and in fact I intend to propose something related to it for R7RS-large in order to do partial evaluation, which is useful in connection with the possible introduction of second-class lexical syntax. More on that another day.
R5RS and R7RS-small do provide global environment objects. The trouble is that there is no way to create fresh objects. The only mutable environment object guaranteed to exist is the interaction environment, and there is no assurance about exactly what names it provides (informally: the names visible at the REPL). What is more, R5RS does not allow evaluating definitions in order to create new bindings, though R7RS does. I have a preliminary proposal to lift those restrictions for R7RS-large.
There is not, nor do I intend to propose, any machinery for first-class lexical environments.
I don't have a problem with multiple return values. In fact if you have both continuations, and functions that take multiple arguments, then they make the semantics more regular and consistent. I'd have expressed them differently but that's bikeshedding. I don't have a problem with them.
And lots of people think Scheme/Lisp macrology is natural and consistent; I think they are wrong, because these features create a staged runtime and its attendant set of complications, and the purposes they serve should probably have been served otherwise (as in Kernel).
Winding continuations on the other hand are in fact an ugly stain. They are a 'bandaid' on a very deep impedance mismatch that needed to be eliminated or resolved in a way that simplified things, rather than bandaged in a way that complicated them.
and getting rid of unnecessary glue boilerplate, having multiple values the way lua does, where both calls AND returns can take different numbers IN THE SAME FUNCTION without an error and MISMATCH WITHOUT AN ERROR is much more convenient. It may be less safe, but getting rid of boilerplate is worth it.
The Lua / Common Lisp rules (extra values are dropped, missing values are set to null) are valid in Scheme, though not a requirement, and a round dozen of Schemes actually apply them. However, not requiring them means that low-rent but conforming Schemes like Chibi can use very simple implementations, because there is no requirement to signal an error on mismatch. Details on multiple values are available.
I've observed the potential neatness of that facet of Lua, and considered its implications for language design in general. Seems to me that while a language design may benefit from neat conceptual devices like this, the benefit is lost if there are too many of them not fundamentally connected to each other. JavaScript has lots of pieces with insufficient overall coherence, making it a tangled mess. Indeed, getting the whole small enough for serious synergy is quite difficult. I've obviously thought deeply about what the core concepts of Lisp are, and it seems to me multiple-value returns don't fit cleanly into the picture. What could be done to expand a coherent Lua-like approach work is a separate (and engrossing) question; indeed, one could say the same for any language with some merit to it. A side project I've been mulling over for many years is to try to isolate and expand the elegant core of vintage 1970s BASIC — it has to have had such a core or would never have been popular.
In fact if you have both continuations, and functions that take multiple arguments, then [multiple return values] make the semantics more regular and consistent.
I submit this is an illusion caused by having got things subtly wrong in the first place. The irregularity is already present, and multiple return values try to generalize from it with inevitably unfortunate results; trying to build a higher and higher tower on a flawed foundation eventually comes to grief, hence the Smoothness Principle I've proposed re abstraction theory (any roughness in a language design ultimately bounds its radius of abstraction). Scheme doesn't allow you to write (apply (lambda x x) 2) even though common sense says this ought to evaluate to 2, because the language design fails to grant first-class status to the argument list passed to a procedure. Once you admit first-class argument lists, you can see that this entire structure is what ought to be passed to a continuation, so that instead of writing (c 2) one ought to write (apply c 2). The idea that there is something "more general" about passing multiple return values to a procedure is grounded in the illusion created by instantiating a continuation as a procedure that takes just one argument and discards the rest of its (second-class) argument list.
(apply (lambda x x) 2)
(c 2)
(apply c 2)
It is not obvious to me that something which accepts a proper list as its argument structure should also accept improper lists, nor is it obvious what the utility of function calls of the form (f a . b) might be.
(f a . b)
The goal is to provide future programmers with a uniform language design that empowers them to imagine things we haven't thought of, by leveraging the uniformity we've given them, and, having thought of those things, to write them and have them work as expected. We expect to be unable to name specifically the ways such features might be used down the road. The fact that (apply (lambda x x) 2) in Scheme doesn't do what we expect it to do is a problem in itself because it deviates from our understanding of the uniform language design; the unacceptability of the deviation does not depend on our ability to name a specific situation where we want that. (I do recall using an improper operand-list in my library implementation of $cond, but the general point stands without that.)
$cond
In building a lisp of my own I decided it would be better if cyclic or improper lists were among the parts of the data representation that do not eval to runnable code. Their use in lambda lists seems like a minor wart to me.
I don't know if eliminating the improper-list lambda arguments would be a good choice for scheme; I certainly wouldn't be bringing it up in a scheme standardization effort because although I like the &listargs sigil better, the issue isn't all that important and most people think of the . as a sigil rather than list structure anyway.
The fact that it's list structure created inconsistencies when I defined 'lambda' as a procedure rather than as syntax. And rather than allowing the inconsistencies to spread and start affecting other things, I used a sigil list element instead. I'm also using other sigils (like &lazy) in lambda lists so it seemed to be the most consistent approach from the user's POV as well.
Scheme has committed to the improper-list formal argument structure for a very long time and, unlike a lot of more important things, does not seem to be causing a lot of wailing and gnashing of teeth. So I'd pass it by unless people were reporting it as a source of pain or limitation.
You are absolutely right when you say it is a failure of 'smoothness' when scheme does not allow something like applying a lambda expression directly.
But that happens because of the function/syntax roughness, not because of any arity roughness, so I don't see how it's an argument against having the same rules for return arity and argument arity.
In terms of arity, I see smoothness in a lambda calculus where a function can only take a single argument and then return a single value. It's even smooth when the single argument is a list of values and the single return is also a list of values. Where the implementation is consistent about boxing and unboxing (ie, never passes or returns a non-list) the multi-argument case is semantically identical to the single-argument case.
But passing a list of arguments one way and not passing a list of returns the other way breaks symmetry, especially where the language has continuations. For perfectly smooth semantics, functions ought to return the same way they're called - ie, the caller should not need to know whether this is a continuation or some other kind of function, should not have to check for and generate special-case code for that case, and should not need to know whether its own call stack is going to get garbage-collected after making the call. It just does what it does to call a function, and that's it.
If you want multiple arguments and single returns, that's smooth in the *absence* of continuations. And continuations are a bit of a semantic minefield in the first place, and a simple call stack with tail recursion is very general. So smoothness achieved without continuations would not make a language at all crippled.
I didn't give a complete argument against multiple-value returns; I touched lightly on a few parts of it. Continuations come into it because the way continuations are applied in Scheme encourages the misconception that leads to multiple-value returns; but even without continuations the misconception would still be possible. The basic notion behind multiple-value returns is that returning multiple values would be "more general than" returning just one. But if returning multiple values is more general than returning just one, wouldn't returning a first-class list of all the return values be "even more general than" multiple-value return? Of course it would, but doing so would seem silly because in that case why not just return the whole list as a single result. And indeed, it would be silly and one should just return the whole list as a single result. It should be clear that this is all just a question of how you want to arrange the syntax for returning multiple values — and that's a point on which Scheme is weak. Indeed, I seem to recall seeing the same weakness in Backus's "Can Programming Be Liberated from the von Neumann Style?": although in theory a computation that produces multiple results can be handled by a functional expression that evaluates to a tuple, in practice that only works if you have syntax for very conveniently taking the tuple apart once it's been returned. Kernel does have such syntax: generalized definiends. In Kernel when you have a procedure p that returns a list of four values, you can write
p
($define! (a b c d) (p ...))
and those four values will be bound to symbols a, b, c, d. Scheme can't do that because it's overloaded its define syntax with some unfortunate "syntactic sugar" for defining procedures. (From some things I've heard about introductory Scheme classes, that syntactic sugar also tends to sabotage students' understanding of the elegant concepts behind Lisp, by encouraging them to think of procedures as second-class language elements.)
a
b
c
d
define
So what we're really dealing with is a very deep design choice that might seem to be a "simple" question about the syntax of function value return, but really has sweeping consequences across the whole design. Making it difficult to give a compact explanation of the choice.
... with the admittedly lame syntax sugar for defining procedures, we have to name our general multiple-value operators somewhat noisily: define-values, let-values, and let*-values. They've been around for 15 years and are part of R7RS-small. That seems a minor thing to make a fuss about.
Uniformity looks like a small thing if you look for one small place where it'll make a huge difference. But it's ubiquitous, and has these individually seemingly-not-earthshaking effects that add up until, in the long run, its cumulative effect overwhelms everything else. Even then one might fail to notice it, because the effect is then on such a big scale, like failing to notice that you're standing on a continent.
If I were to complain about scheme I'd pick the lack of convenince:
1) arrays don't grow for you. Why? WTF why?
2) records have an interface that's so bad it looks like it's from the 50s
3) basic syntactic sugar are through things that once again are so crazy like make-set-tranformer or set-variable-transformer that I want to run screaming
4) the new macro system is horrible for everything except a few simple examples from someone's paper. Forget things being able to implement an object system with instance variables visible in methods.
5) despite protestations to the contrary syntactic tokens have hidden fields that you can't examine or set properly, such as the all important one that specifies what context a variable is in - at best you can just pick a token at random from the source and make a new token based on it and hope it's at the right level... Damn it's so bad.
I mean you're right about uniformity, but wrong that your example is a bad one
1) Arrays don't grow for you because efficiency, and because you can easily layer growing arrays over non-growing ones.
2) In the 1950s records looked like this:
01 MAILING-RECORD.
05 COMPANY-NAME PIC X(30).
05 CONTACTS.
10 PRESIDENT.
15 LAST-NAME PIC X(15).
15 FIRST-NAME PIC X(8).
10 VP-MARKETING.
15 LAST-NAME PIC X(15).
15 FIRST-NAME PIC X(8).
10 ALTERNATE-CONTACT.
15 TITLE PIC X(10).
15 LAST-NAME PIC X(15).
15 FIRST-NAME PIC X(8).
05 ADDRESS PIC X(15).
05 CITY PIC X(15).
05 STATE PIC XX.
05 ZIP PIC 9(5).
Not Scheme, I assure you.
3) That's Racket-specific.
4) Identifier-syntax macros can and do handle "instance variables visible in methods". I personally think that when you see a variable, a variable it should be and not a disguised method call, but the capability exists in R6RS.
5) That's syntax-case-specific. Despite R6RS, syntax-case is not and never has been the only low-level macro system.
It is exactly as you say. A single argument - which is a list. And a single return - which is also a list. Makes it exactly equal to the one-argument lambda calculus. Neither more nor less general. I wasn't arguing about generality, I was arguing about call/return semantics mismatch. Smoothness fails at the semantic level if there is a mismatch where one is *always* a list and the other might not be.
The syntactic failure here is only that Scheme doesn't make it as easy to accept multiple returns as it is to pass multiple arguments. For me that comes under "yes the syntax is a shame, but no the semantics aren't wrong."
I suggest asking those who did it why they pursued IEEE standardization in the first place. If they are not teetotalers, perhaps get a few drinks into them first. Ask: Are those reasons relevant today? Were the broader goals of IEEE standardization actually achieved? In retrospect, does it seem worth it (a) personally, (b) for the future development of research, development, and use of scheme. Cui bono? Quid?
Scheme would be a different and, I think, more interesting language these days if Steele's advisors had looked at the Rabbit thesis and said "It's a bit thin. Add a second half about dynamically interpreted Scheme and reflective features made possible in an interpreter."
Instead, the authorities since r4rs have seemed hell bent on making sure that any such dynamic features are Not Scheme. At the same time, they keep raising the bar of what a complete implementation is supposed to comprise.
While that's what the authorities are up to, no small part of (what remains of) actual real world interest in Scheme seems to concern flyweight implementations and the use of Scheme for dynamically programming interactive environments. Go figure.
One reason for pursuing standardisation for Scheme (and for Common Lisp) back then was a fear that otherwise someone else would initiate a standardisation process and would consequently have more control over the resulting language definition.
Both Scheme and Common Lisp had an informal group working on what the language should be, and standardisation in effect took those groups and turned them into the technical committees for the standardisation efforts.
The danger wasn't only from potential standards for the very same language (Scheme or Common Lisp) but also from ones that would seem to cover those languages, so that it wouldn't make sense for them to have a separate standard. One of the reasons the ISO standard is for ISLisp, rather than Lisp, is that the Americans were adamant that there mustn't be a standard for all of Lisp -- indeed, McCarthy said he would denounce any such standard -- and that Lisp be treated as a family of languages which could have separate standards, rather than as one language.
Another reason for pursuing standardisation, at least for Common Lisp, was that some funding bodies preferred or required the use of applicable standards. That put languages that were not standardized (or, rather, people who wanted to use those languages) at a disadvantage.
Another reason for pursuing standardisation, at least for Common Lisp, was that some funding bodies preferred or required the use of applicable standards. That put languages that were not standardized (or, rather, people who wanted to use those languages) at a disadvantage.
Sure, Common Lisp was clearly an attempt to draw the boundary lines between commodity forms to prevent lock-in to particular lisp vendors. It could be compared by analogy to the way POSIX was meant to resist lock-in to particular unix vendors.
The thing about Scheme is that it never actually encountered the threat of lock-in because no implementation of Scheme at any point in its entire history have ever had quite the economic importance of any of the commercial lisp machines (nevermind a unix). There's something cargo-cultish about standardizing it.
McCarthy said he would denounce any such standard -- and that Lisp be treated as a family of languages which could have separate standards, rather than as one language.
I had no idea. Smart guy.
If the reason the last RnRS failed to adapt to the new realities of unicode was a desire to be consistent with the IEEE standard, then it is best to allow the IEEE standard to die, so that the mistake is not repeated.
However, I fear that having already standardized on the Wrong Thing, they will not correct their errors in that regard. Nor will they make a choice between flow-of-control paradigms; now that throw/catch and exceptions have been forced into the language, they are going to fight unto Scheme's death against continuations - particularly against winding continuations, which are a stain on the language in their own right.
if the RnRS branch has gone irretrievably wrong, would that then be a reason to ignore it and strive to get the IEEE branch right?
After doing all the work, you need to send out ballots to the electors, and get a 75% return on ballots and a 75% approval rate. "Politics is the art of the possible." (Peter Medawar)
Figuring out what one wants to happen is prerequisite to any political effort, however imperfect, to make it happen. It's not possible even to approximate achievement of goals one hasn't identified.
Do you imagine that because the IEEE withdraws its official approval, the P1178 document (or R4RS+, whatever) ceases to exist? For every Schemer who wants Scheme to "adapt to the new realities of Unicode", there are at least two Schemers who think the ASCII repertoire (not even the ASCII encoding) is the perfect, jewel-like counterpart to small Scheme. Everything beyond ASCII is standardized but optional in R7RS, and that's what was needed in order to get to consensus. (The fact that ASCII, like Unicode, was a political compromise is simply forgotten.)
With a less conservative Steering Committee, I would have been happy to make R7RS a more radical break with the pre-Unicode past. But the community elected that Committee, and presumably got what it expected to get. There is no "gray They" here, just John Cowan and Alex Shinn and Art Gleckler and all the WG1 members and all the people who voted either for or against R7RS.
Ah well, "the part-time help of wits is no better than the full-time help of halfwits." (Wolcott Gibbs, I think) | http://lambda-the-ultimate.org/node/5324 | CC-MAIN-2019-43 | refinedweb | 12,598 | 58.21 |
In one of my previous posts about Command-Query Separation (CQS) and side effecting functions being code smells, it was pointed out to me again about immutable builders. For the most part, this has been one area of CQS that I've been willing to let break. I've been following Martin Fowler's advice on method chaining and it has worked quite well. But, revisiting an item like this never hurts. Immutability is something you'll see me harping on time and time again now and in the future. The standard rules I usually do is immutable and side effect free when you can, mutable state where you must. I like the opt-in mutability of functional languages such as F# which I'll cover at some point in the near future instead of the opt-out mutability of imperative/OO languages such as C#.
Typical Builders
The idea of the standard builder is pretty prevalent in most applications we see today with fluent interfaces. Take for example most Inversion of Control (IoC) containers when registering types and so on:
UnityContainer container = new UnityContainer();
container
.RegisterType<ILogger, DebugLogger>("logger.Debug")
.RegisterType<ICustomerRepository, CustomerRepository>();
Let's take a naive medical claims processing system and building up and aggregate root of a claim. This claim contains such things as the claim information, the lines, the provider, recipient and so on. This is a brief sample and not meant to be the real thing, but just a quick example. After all, I'm missing things such as eligibility and so on.
public class Claim
{
public string ClaimId { get; set; }
public DateTime ClaimDate { get; set; }
public List<ClaimLine> ClaimLines { get; set; }
public Recipient ClaimRecipient { get; set; }
public Provider ClaimProvider { get; set; }
}
public class ClaimLine
{
public int ClaimLineId { get; set; }
public string ClaimCode { get; set; }
public double Quantity { get; set; }
}
public class Recipient | http://www.eggheadcafe.com/aspnet/how-to/2798072/commandquery-separation.aspx | crawl-001 | refinedweb | 309 | 50.26 |
A NotifyResult object holds the notification information in the Streams AQ notification callback. It is created by OCCI before invoking a user-callback, and is destroyed after the user-callback returns.
Gets the name of the consumer for which the message has been enqueued. In case of a single consumer queue, this is a empty string.
string getConsumerName() const;
Gets the message which has been enqueued into the non-persistent queue.
Message getMessage() const;
Gets the id of the message which has been enqueued.
Bytes getMessageId() const;
Gets the payload in case of a notification from
NS_ANONYMOUS namespace.
Bytes getPayload() const;
Gets the name of the queue on which the enqueue has happened
string getQueueName() const; | http://docs.oracle.com/cd/B14117_01/appdev.101/b10778/reference019.htm | CC-MAIN-2014-10 | refinedweb | 116 | 57.16 |
For code/output blocks: Use ``` (aka backtick or grave accent) in a single line before and after the block. See:
How can I plot the broker value vs a stock?
- Eduardo De La Garza last edited by
I have been able to plot the AAPL stock and the value on different charts. I would like to have them on the same chart so I can compare them. How can I do that? I don't know if I can add a value indicator to the data or what. This is what I have.
import datetime # For datetime objects import os.path # To manage paths import sys # To find out the script name (in argv[0]) # Import the backtrader platform import backtrader as bt from _extensions.data_definitions import DOHLCVData AAPL_PATH = "./../../data/datasets/02_processed/eod/AAPL.csv" class LongAAPL(bt.Strategy): def next(self): self.order_target_percent(self.data, 1) if __name__ == '__main__': # Create a cerebro entity cerebro = bt.Cerebro(stdstats=False) # Create a Data Feed data = DOHLCVData( dataname=AAPL_PATH, headers=True, fromdate=datetime.datetime(2020, 1, 1), todate=datetime.datetime(2020, 12, 31), # month was in 12 reverse=False ) cerebro.adddata(data, name="AAPL") cerebro.broker.setcash(100000.0) cerebro.addobserver(bt.observers.Value) cerebro.addstrategy(LongAAPL) print('Starting Portfolio Value: %.2f' % cerebro.broker.getvalue()) # Run over everything cerebro.run() # Print out the final result print('Final Portfolio Value: %.2f' % cerebro.broker.getvalue()) cerebro.plot()
- Eduardo De La Garza last edited by
Of course right now the lines would be the same since I'm buying AAPL 100% but I want so I can see the results after modifying the strategy. Thanks!
Articles - Benchmarking
Docs - Observers - Benchmarking | https://community.backtrader.com/topic/2758/how-can-i-plot-the-broker-value-vs-a-stock | CC-MAIN-2020-34 | refinedweb | 275 | 52.66 |
Tres Seaver wrote: > SVN Reorganiztion > ----------------- > > I just worked a bit today on spliting CMF 2.1.0 (GenericSetup 1.3.2) out > into separately releasable egg-based distributions. For the initial > pass, see: > > svn://svn.zope.org/repos/main/Products.GenericSetup/tags/1.3.2 > > Note that the SVN URL above is not the same as the one we've been using > (svn://svn.zope.org/repos/main/GenericSetup) and that it adds the > additional "namespace" package ('Products') to the checkout. I plan > to fix up the externals currenly pointing into '/GenericSetup' in the > CMF trunk and 2.1 branch, and then make '/GenericSetup' empty, with a > pointer to the new location. > > Egg Releases > ------------ > > I uploaded the Products.GenericSetup 1.3.2 egg to the Cheeseshop: > > > > The egg should be 'easy_installable' in any environment with setuptools > installed; if that environment has a properly-namespaced 'Products' > package (Zope2 trunk, or with the backport I'm proposing for Zope issue > #2359), it should Just Work. > > Further Work > ------------ > >?
Advertising
Big +1 :) Hanno _______________________________________________ Zope-CMF maillist - Zope-CMF@lists.zope.org See for bug reports and feature requests | https://www.mail-archive.com/zope-cmf@lists.zope.org/msg04504.html | CC-MAIN-2016-44 | refinedweb | 185 | 50.23 |
So far we have defined data, and we have seen that our data can be displayed in our browser, but will our users like reading raw information? We will now begin to learn how to display XML. Note: we will not be teaching Cascading Style Sheets (CSS) here; we saw the basics of CSS in the previous chapter. We discuss only how to use them with XML.
Using CSS serves several purposes:
It improves clarity of the document when displayed.
We can write once, use often.
One change can be reflected many places.
We can present the same data in different ways for different purposes.
With a style sheet all the display rules are kept in one file that is linked to the source document. So we need to define what our display rules will be and associate them with our XML tags.
Create a new file called pdalist.css and type the following:
name { DISPLAY: block; FONT-WEIGHT: bold; FONT-SIZE: 20pt; COLOR: #9370db; FONT-FAMILY: Arial, verdana; } os { DISPLAY: block; FONT-SIZE: 16pt; COLOR: #9370db; FONT-FAMILY: Arial, verdana; } processor { DISPLAY:inline; FONT-SIZE: 14pt; COLOR: #9370db; FONT-FAMILY: Arial, verdana; } color { DISPLAY: inline; FONT-WEIGHT: bold; FONT-SIZE: 12pt; COLOR: #c71585; FONT-FAMILY: Arial, verdana; TEXT-ALIGN: Left; } height { DISPLAY: inline; FONT-STYLE: italic; FONT-SIZE: 10pt; COLOR: #9370db; FONT-FAMILY: Arial, verdana; } width { DISPLAY: inline; FONT-STYLE: italic; FONT-SIZE: 10pt; COLOR: #9370db; FONT-FAMILY: Arial, verdana; } ram { DISPLAY: inline; FONT-STYLE: italic; FONT-SIZE: 10pt; COLOR:#c71585; FONT-FAMILY: Arial, verdana; } rom { DISPLAY: inline; FONT-STYLE: italic; FONT-SIZE: 10pt; COLOR:#c71585; FONT-FAMILY: Arial, verdana; } price { DISPLAY:block; FONT-SIZE: 8pt; COLOR:#c71585; FONT-FAMILY: Arial, verdana; }
Here we have defined blocks of style to match our elements that have data. We have name, os, processor, color, height, width, ram, rom, and price. Each one of these defined elements in our XML file contains data to be displayed. Our elements, pdalist, pda, screen, pixels, and memory, are parent (node) elements. Defining styles for both in all instances would be redundant because the child definitions will take precedence over the parent element definitions. The element names we use here are the pattern-matching sections in the CSS. These will match up to our XML elements.
What makes a style work are the properties, which are between the curly braces { }. Action is taken against the matched element. Starting with our name element we have the following properties: Display, Font-Weight, Font-Size, Color and Font-Family, and many other properties. But Display is new. What does this mean? Inside the browser is a CSS forms areas, the first is the PAGE. This is the page we see when HTML or XML is rendered. Inside the page, nested, are several AREA blocks and inside an AREA are BLOCK and FLOW objects. With the CSS property, we can specify a style for the page, an area, and even a block or a flow area.
A block value for display will place that element on its own line. An inline value will display the next element on the same line as the previous one. Our elements name and os will be on separate lines because they are declared as blocks. Processor is inline, as are color, height, width, ram, and rom. Price is a block so this will be on a separate line.
All properties are specified with a colon, which delimits the property from the value. All property declarations end with a semicolon.
We could also write it so the parent element has the style defined.
name { DISPLAY: block; FONT-WEIGHT: bold; FONT-SIZE: 20pt; COLOR: #9370db; FONT-FAMILY: Arial, Verdana; } os { DISPLAY: block; FONT-SIZE: 16pt; COLOR: #9370db; FONT-FAMILY: Arial, Verdana; } processor { DISPLAY:block; FONT-SIZE: 14pt; COLOR: #9370db; FONT-FAMILY: Arial, Verdana; } screen { DISPLAY: block; FONT-WEIGHT: bold; FONT-SIZE: 12pt; COLOR: #c71585; FONT-FAMILY: Arial, Verdana; TEXT-ALIGN: Left; } memory { DISPLAY: block; FONT-STYLE: italic; FONT-SIZE: 10pt; COLOR: #9370db; FONT-FAMILY: Arial, Verdana; } price { DISPLAY:block; FONT-SIZE: 8pt; COLOR:#c71585; FONT-FAMILY: Arial, Verdana; }
Save this as pdalist2.css.
We now have our pdalist.xml and a pdalist.css. We need to tie the two together so we can display our XML with style!
We need to make a declaration in our XML file so when it loads, the CSS file can be used. Let's open our pdalist4.xml file and add the following line after our XML declaration. Save this file as pdalist4.xml.
<?xml-stylesheet href="pdalist.css" type="text/css"?>
When we open our XML file in IE, we should see the screen shown in Figure 14-6.
Figure 14-7 shows how our file will look in Netscape.
You can see that the elements for color, height, and width all have the same formatting, unlike our screenshot in Figure 14-7. This is because we defined our parent element screen, and it cascades down to the subelements.
Change the style sheet declaration to the following, so we can use our second CSS.
<?xml-stylesheet href="pdalist2.css" type="text/css"?>
Go back and look at what we did for our pdalist2.css. All elements are to display as blocks, but also take note that we defined styles for those elements that had subelements: memory, which has ram and rom; screen, which has color; and pixels, which has the subelements height and width. Figure 14-8 shows what our display will look like in Netscape, and Figure 14-9 shows our results in IE.
Let's look at how we can use XSL to format the results of the XML parsing.
XSLT is a template-based programming language that allows us to restructure our content to create the look we require. XSLT transformations can enable different kinds of software applications to exchange data. They can also be used to generate multiple views of the same source document to enable a website's content to be displayed on a myriad of devices.
XSLT's elements and attributes provide a declarative programming language for processing XML data. We can use XSLT's vocabulary to grab content from other documents, create new elements and attributes or, more commonly, some combination of the two.
An XSLT 1.0 transformation requires two starting documents (an XML source document and an XSLT style sheet) to produce a single result document. Note that the forthcoming XSLT 2.0 won't require this. The process begins when an XSLT style sheet is applied to an XML document's source tree to generate a result tree that is usually saved as an XML or HTML document. (See Figure 14-10.)
Note I have simplified our original example and removed the screen elements.
An XSLT style sheet contains template rules that define the following:
The criteria for selecting elements from the source tree
Instructions for restructuring the selected content to create the result tree
Template rules are the key building blocks of XSLT transformations. A template rule has two parts: a pattern and a template. The pattern (usually an element name) is then matched against elements in the source tree to determine which nodes to select for processing. The template provides instructions for processing the selected content.
Each template rule constructs a result tree fragment of markup and content. An XSLT transformation's result tree is created when all of the result tree fragments are combined in the order specified to form a completed whole.
Now let's go through an example style sheet and get into more detail about XSLT's template rules.
Our XSLT style sheet document needs to include an XML version declaration (just like any other XML document.
<?xml version="1.0" encoding="iso-8859-1"?>
Next, we will declare XSLT's namespace prefix. XSLT's namespace-prefixed elements enable an XSLT processor to distinguish them from other kinds of markup in the style sheet, such as the HTML elements contained within a template rule.
XSLT's namespace prefix is declared within the stylesheet's root element, which is allowed to be either xsl:stylesheet or xsl:transform.
An XSLT version attribute should be included between the root element and the xsl namespace-prefix declaration.
The XSLT namespace is identified by its unique URI value (), not by the xsl prefix.
<?xml version="1.0" encoding="ISO-8859-1"?> <xsl:stylesheet
Now that we have our namespace prefix declared, we can go about creating some template rules that will be used to transform our source glossary document into an HTML table. Much like an old fashioned mail merge, the HTML markup fragments in the following template provide the XSLT processor with a model for restructuring our source content.
The xsl:template element is used to encapsulate template rules. The value of its match attribute contains an XPath statement that is used as a pattern to select source elements for processing. A document's first template almost always has a match value of /, which means the document root.
<?xml version="1.0" encoding="ISO-8859-1"?> <xsl:stylesheet <xsl:template <html> <head> <title>Review Of Palm PCs</title> </head> <body> <h4>List Of Palm/Pocket PCs</h4> <table width="100%" border="1"> <thead> <tr> <th>Name</th> <th>OS</th> <th>Processor</th> <th>Memory (RAM/ROM)</th> <th>Price</th> </tr> </thead> <tbody> <xsl:apply-templates/> </tbody> </table> </body> </html> </xsl:template>
The apply-templates element signals an XSLT processor to look for other template rules and apply them at that point in the style sheet's structure. The results of each rule combines to form the result tree of the completed transformation.
The following template matches each <pda> entry in the XML pdalist file, and creates table rows until it runs out of item elements to process.
>
Notice how the value-of element also uses a select attribute to choose the content from the source document we wish to use to create our result document.
Our finished XSL file should look like this:
<?xml version="1.0" encoding="ISO-8859-1"?> <xsl:stylesheet <xsl:template <html> <head> <title>Review Of Palm PCs</title> </head> <body> <center><h4>List Of Palm/Pocket PCs</h4></center> <table width="100%" border="1"> <thead> <tr> <th>Name</th> <th>OS</th> <th>Processor</th> <th>Memory (RAM/ROM)</th> <th>Price</th> </tr> </thead> <tbody> <xsl:apply-templates/> </tbody> </table> </body> </html> </xsl:template> >
Be sure to save it as pdalist.xsl.
An XML processing instruction is used to associate an XML document with a Cascading Style Sheet (CSS) or XSL Transformations (XSLT) style sheet. The syntax used is identical except for the value of the type attribute, which will be either "text/css" or "text/xsl" depending on which flavor style sheet is used.
Following are the two variations side-by-side to illustrate the different values of the type attribute.
<?xml-stylesheet type="text/xsl" href="pdalist.xsl"?> <?xml-stylesheet type="text/css" href="pdalist.css"?>
The correct placement of the style sheet declaration is within a document's prologue (after the XML declaration and before the root element).
Now we need to alter our .xml file and tell it to refer to the .xsl file. Open up pdalist4.xml and alter the top part as shown here:
<?xml version="1.0" encoding="iso-8859-1"?> <?xml-stylesheet <pdalist> <pda> .. ...
Apart from deleting the reference to our .css file and adding a reference to the .xsl file, the remainder of the file remains the same. Save the file as pdalist5.xml and load it into IE, and we'll see the page shown in Figure 14-11.
Loaded into Netscape 7, we see the page shown in Figure 14-12.
It has to be said that IE 6 is much more descriptive in its error details if we do make a mistake. Netscape generally just tells us a mistake has been made but leaves it up to us to find out where. | http://www.yaldex.com/javascript_tutorial_3/LiB0101.html | CC-MAIN-2018-26 | refinedweb | 1,996 | 62.88 |
I am just coming to haskell, and I wrote a simple command to get some input from a pdf file I just wanted the output of the command so I did something like import System.Process (runInteractiveCommand) import IO (hGetContents) -- | returns the text of the first page of the pdf at the given path, needs pdftotext getTextOfPdf :: String -> IO String getTextOfPdf pdfPath = do (inp,out,err,pid) <- runInteractiveCommand ("pdftotext -l 1 "+ +pdfPath++" -") return (hGetContents out) I don't care about error handling, if something goes wrong it is ok to hang or crash, but knowing unix I wondered if this would do the right thing or if it would create a zombi process. I was about to ask, but then I thought "let's test it", and sure enough the zombi stays there. I tried to even to allocate more than one, wait, I even managed to exhaust the resources of my machine... So here is what I would have liked to happen: when the pid gets garbage collected it tries to wait for the process, and if that fails the pid stays around longer and will try to wait later. Too difficult? I don't know, but it is what I had expected from haskell. Failing that I would have expected clear hints that one should wait for external processes in the documentation, and I found none. So what is the way out? I could do a forkIO and wait for the process but then I wonder do I have to wait for the thread, or dead thread become zombi? I that is the case then the only way out would be to give back also the pid and make the waiting responsibility of the caller, not very nice, but probably the real solution. I have seen that in missingh there is a pipeout example but it seems to me that you are still responsible to wait for the process (with ensureSuccess). Maybe the correct thing is not being able to ignore the return code of the process.... but now I am becoming suspicious of other things, for example a file handle, you need to close it or you can expect that it will be closed when the handle is garbage collected? Are there other places where you need to pay attention to be sure that you are releasing the resources you acquired? I suppose problems can come only when an external resource is involved, or not So 1) documentation should specify if one should do some specific action to free resources, can someone fix this? 2) is there a clean (haskell;) way to deal with this? 3) other places apart external processes where you have to pay attention? What is your wisdom... thanks Fawzi | http://www.haskell.org/pipermail/haskell-cafe/2007-February/022236.html | CC-MAIN-2014-42 | refinedweb | 456 | 71.58 |
Confessions of a Converted PHP Developer: Namespace Superhero!.
Namespaces are a way of encapsulating code to a specific library or area. This is most easily viewed as a way to create classes that are unlikely to conflict with other classes. If you had a class called foo, and then started using a library of classes which also included a class called foo, then you’re in trouble, as you’ve now got two classes with the same name. In PHP you’d end up with an ugly error – which is actually quite good, as you’re able to track it down. In Ruby you’d just end up with a frankenstein of the two classes in one — which is definitely not good.
To get around this issue, programming languages need a way to group together like items into their own encapsulated area so that one domain of your code can have the same classes as another domain of your code. The term for one of these groups is namespace.
Namespacing has been a core part of Ruby since it’s inception — just not officially under that name — whereas in PHP it’s a relatively new addition. As a result of this there’s a semi defacto naming convention in many of the PHP libraries that maps classes to folders as a form of namespacing. While this works to create unique classes, it also makes the code somewhat verbose and unsightly.
PHP’s lack of namespacing
PHP only introduced proper namespacing in version 5.3, released at the end of June 2009 to much furore and, from my experience, has been very slow in uptake. I’d attribute this to one main fact, and that’s backwards compatibility. Unfortunately the hosting community’s uptake of new versions of PHP is very slow, and as such the availability of PHP 5.3 to a large proportion of the user base is not there. PHP 5.3 accounts for under 9% of websites known to be using PHP. For a developer to use namespaces in their library they’re effectively cutting off a large user base, and while that’s no excuse to stifle a feature’s use — you can understand why some developers are loathe to do it.
PHP’s Psuedo Namespacing
Before official namespace support was available in PHP, it was common to define your classes with a sort of psuedo-namespace based on the folder structure of your classes, adding underscores to distinguish new folders or files.
An example of a library that uses this method is the library Facade.
Facade’s file structure
We can see there is a
Request.php file in the
Facade/S3 folder. Following the psuedo namespacing we end up with a class named
Facade_S3_Request. This also makes it easy for auto loaders to find a file to load. If you ask for
Facade_S3_Request it’s easy to look for
Facade/S3/Request.php.
This works well, except you’re stuck having to use the verbose class names in both the libraries’ code and the code that has to use it. This can get a little ugly when you start using large codebases — here’s a class name in a library I use:
HTMLPurifier_AttrDef_URI_Email_SimpleCheck.
PHP’s Official Namespacing
Namespaces are defined by using the
namespace keyword right at the top of your PHP file (it has to be there), like so:
<?PHP namespace Foo; // or alternatively namespace Foo{ # code here }
All code after the
namespace Foo; command will be in the Foo namespace.
You can also assign sub namespaces by separating them with a backslash character.
<?PHP namespace FooBar; class MyClass { public function hello() { return "Hello World"; } }
Now you could use this code in one of two ways, firstly:
<?PHP include 'my_class.php'; // Let's assume our previous code is in this file echo FooBarMyClass::hello();
This uses the fully qualified namespace to reference the class, or secondly:
<?PHP use FooBar; include 'my_class.php'; // Remember our assumption from before... echo BarMyClass::hello();
We tell PHP that we want to use the
FooBar namespace, and then we call
BarMyClass. You might have thought we’d just be able to call
MyClass without the
Bar part, and while that makes sense — it’s just not the case.
It only really makes sense if you look into the way PHP namespaces are aliased.
use FooBar is the same as saying
use FooBar as Bar — which means that
Bar is aliased to
FooBar. You could say
use FooBar as Potato and then call
echo PotatoMyClass::Hello(). Confusing? Yes. Useful? To a degree.
There’s a bunch of rules to do with precedence and a few more features but I’ve rabbited on about PHP for enough. You’re here for Ruby, so let’s look at how Ruby implements namespaces. You can read more about PHP’s namespaces in this series of SitePoint articles.
Ruby modules, er… namespaces!
We’ve already seen Ruby modules in action while talking about mixins, but they’re also Ruby’s built in way of creating namespaces.
A basic namespace
module Good class Person def self.Welcome puts "Well, Hello World!" end end end module Evil class Person def self.Welcome puts "I will kill ye' all." end end end
We now have two modules with separate
Person classes, each with their own
Welcome method. We can access these by using the standard module operator.
Good::Person.Welcome > "Well, Hello World!" Evil::Person.Welcome > "I will kill ye' all."
Alternatively we can include this into another class, and drop the module name.
class HelloWorld include Good def self.WelcomeMessage Person.Welcome end end HelloWorld.WelcomeMessage > "Well, Hello World!"
So what we’ve done there, is create a new class which includes the
Good module. Inside the
WelcomeMessage class method we simply call
Person.Welcome and since we’ve included the
Good module,
Person refers to
Good::Person.
Applying multiple ‘namespaces’
This method of namespacing is interesting, as it allows you to apply multiple modules with the
include statement, and the methods will simply overwrite each other, but leave methods that aren’t available in a later module alone. We can see this by doing two things. First we’ll add a new class to the
Good module, and call that in our
WelcomeMessage method inside the
HelloWorld class, and secondly we’ll tell the
HelloWorld class to include
Evil — which will overwrite any classes from
Good which are also in
Evil.
module Good class Animal def self.Welcome puts "Meow." end end end class HelloWorld include Evil def self.WelcomeMessage Person.Welcome Animal.Welcome end end HelloWorld.WelcomeMessage > "I will kill ye' all." > "Meow."
So the output we’re seeing here is a mixture from both
Good and
Evil. We first included
Good, which gave us the
Person and
Animal classes, but when we included
Evil it overwrote the
Person class — but not the
Animal class, since there wasn’t one defined in
Evil. Boom!
Nesting Modules
Modules in Ruby are quite versatile, you can nest them inside each other to build up multiple level namespaces (technically you can nest them in classes too, as
Class is a subclass of
Module, but baby steps eh?).
module SuperHeroes module JusticeLeague class Batman end class Superman end end module Avengers class IronMan end class CaptainAmerica end end end
Here we’ve created a module
SuperHeroes as a super namespace, then created two sub modules
JusticeLeague and
Avengers as sub namespaces. Each of these sub namespaces have a couple of super heroes defined as classes in them.
We can now include either one of those sub namespaces in another class, for example:
class MyHeroes include SuperHeroes::Avengers end MyHeroes.constants > [:IronMan, :CaptainAmerica]
I’ve included the Avengers into my
MyHeroes class, and then listed the available constants (In this case, the classes that were included). It gives us
IronMan and
CaptainAmerica.
Module / Class Short Cuts
You can shortcut your module or class naming, if you know that the module has already been created. If we continue on from before, we can create a new module with this shorthand.
module SuperHeroes::SHIELD class NickFury end end
And that works fine, but only because we have already defined the
SuperHeroes module. If I try and do this without a predefined module, I’ll get an error.
module IHave::NoFriends end > NameError: uninitialized constant Object::IHave
That’s all folks
Today we’ve had an introduction look at ways to namespace your code in Ruby, and how very, very different it is to PHP. I’ve only really scratched the surface when it comes to Modules in Ruby, they’re a truly versatile and complex beast!
If you’ve got any tips on working with Modules, let us know in the comments!
- IT Mitică
- Cody Christofferson
- David
- opensourceame | http://www.sitepoint.com/confessions-of-a-converted-php-developer-namespace-superheroes/ | CC-MAIN-2014-52 | refinedweb | 1,468 | 63.39 |
Odoo Help
This community is for beginners and experts willing to share their Odoo knowledge. It's not a forum to discuss ideas, but a knowledge base of questions and their answers.
Customer: Advanced search filter not working?
In OpenERP V7, the advanced search filter is not working.
For example, if I want to select all customers with "Customer Payment Term is equal to Cash" or "Customer Payment Term contains Cash", the result shown is always the same. The filter is not working at all.
Same effect when trying to filter on a Sale Pricelist. Whatever is filled out in the filter, always all customers are shown.
How to solve this?
Hi,
we can implement advance search for sale pricelist by defining a fnct_search .
'property_product_pricelist': fields.property( 'product.pricelist', type='many2one', relation='product.pricelist', domain=[('type','=','sale')], string="Sale Pricelist", view_load=True,fnct_search=_search_prodt_price, help="This pricelist will be used, instead of the default one, for sales to the current partner"),
Like this we can define this function
def _search_prodt_price(self, cr, uid, obj, name, args, context=None):
return must be in the format return [('id','in',[1,3,5])]
Thanks
Parv is the datatype of Customer Payment Term? Did you try to use the ID instead of String value?
Where can I find this, I'm just a user? I only tried the string values which exist / I have added.
On which object do you try to filter? Customer? AND What is your right access on system? can you connect with admin login?
Yes, customer. I can set the filter to "Companies", "Contacts" (pre-defined filters), everything o.k. I can fill out a name in the search box (right-top), everything o.k. But searching for above mentioned specific data fails.
And I can logon as admin, obviously the advanced search should work also for "normal" users.
It's just to search the id of your search item.
I can't use the filter. sorry | https://www.odoo.com/forum/help-1/question/customer-advanced-search-filter-not-working-16826 | CC-MAIN-2016-50 | refinedweb | 327 | 75.71 |
IRC log of webfonts on 2010-12-01
Timestamps are in UTC.
15:00:25 [RRSAgent]
RRSAgent has joined #webfonts
15:00:25 [RRSAgent]
logging to
15:00:27 [trackbot]
RRSAgent, make logs world
15:00:27 [Zakim]
Zakim has joined #webfonts
15:00:29 [trackbot]
Zakim, this will be 3668
15:00:29 [Zakim]
ok, trackbot; I see IA_Fonts()10:00AM scheduled to start now
15:00:30 [trackbot]
Meeting: WebFonts Working Group Teleconference
15:00:30 [trackbot]
Date: 01 December 2010
15:01:00 [Zakim]
IA_Fonts()10:00AM has now started
15:01:06 [Zakim]
+Tal
15:01:50 [sylvaing]
sylvaing has joined #webfonts
15:02:06 [Zakim]
+ChrisL
15:02:30 [ChrisL]
I started on a disposition of comments
15:02:31 [Zakim]
+tal.a
15:02:32 [erik]
erik has joined #webfonts
15:03:16 [Zakim]
+ +1.978.790.aaaa
15:03:39 [ChrisL]
zakim, aaaa is Vlad
15:03:39 [Zakim]
+Vlad; got it
15:04:19 [ChrisL]
zakim, who is here?
15:04:37 [Zakim]
On the phone I see Tal, ChrisL, tal.a, Vlad
15:04:51 [Zakim]
On IRC I see erik, sylvaing, Zakim, RRSAgent, tal, ChrisL, trackbot
15:05:30 [tal]
I had some phone trouble this morning, maybe zakim got confused by me calling in twice?
15:05:40 [erik]
I'm not able to call in today. I'll follow on IRC.
15:05:57 [ChrisL]
Vlad: having internet issues, will join shortly
15:07:26 [Zakim]
-Vlad
15:07:48 [Zakim]
+Vlad
15:09:11 [Vlad]
Vlad has joined #webfonts
15:10:33 [ChrisL]
Topic: epub update
15:10:43 [ChrisL]
scribenick: chrisl
15:11:16 [ChrisL]
Vlad: strong interest in woff support from many participants, but Adobe representative is against WOFF for epub
15:11:54 [ChrisL]
... if publishers want it, they will add it
15:12:50 [ChrisL]
... waiting for response from internal Adobe discussions. May be opposition was based on resource issues
15:13:13 [ChrisL]
Topic: woff metadata comments
15:14:03 [tal]
15:16:04 [ChrisL]
ChrisL: extensibility via namespaces is good for totally open extensibility
15:16:18 [ChrisL]
tal: we dont want it totally open ended
15:17:05 [ChrisL]
Vlad: want to not deviate too much from the original, and widely deployed, submission. This would be a breaking change
15:17:21 [ChrisL]
... and we do have an extensibility element
15:17:54 [ChrisL]
tal: fontshop and others are using woff with metadata - making all of those invalid is a problem
15:19:23 [ChrisL]
ChrisL: (explains last call process on getting a response back from commentor)
15:19:36 [ChrisL]
Vlad: dont like a breaking change
15:19:53 [ChrisL]
... dont want to invalidate the usage of early adopters
15:21:26 [ChrisL]
action: chris to respond to erik muller on namespaces in metadata
15:21:26 [trackbot]
Created ACTION-51 - Respond to erik muller on namespaces in metadata [on Chris Lilley - due 2010-12-08].
15:22:35 [ChrisL]
action: chris to respond to erik muller on pronunciation and sorting
15:22:35 [trackbot]
Created ACTION-52 - Respond to erik muller on pronunciation and sorting [on Chris Lilley - due 2010-12-08].
15:23:59 [ChrisL]
ChrisL: adding @url to license text elements is a good idea
15:24:54 [ChrisL]
(generally seem to be in favour of separate urls for license elements)
15:25:13 [ChrisL]
Vlad: additional metadata does not override the license
15:26:41 [ChrisL]
Vlad; link can point to a page with multiple further links
15:27:46 [ChrisL]
ChrisL: woff benefit is being explicit on license. prefer to have option for separate ones
15:27:59 [ChrisL]
Vlad: will discuss with Monotype legal
15:28:37 [ChrisL]
tal: nothing changes for existing users. it adds options
15:29:23 [ChrisL]
ChrisL: important that this is not a breaking change
15:30:21 [ChrisL]
Vlad: easier for distributors to use a single place provided by the font owner
15:31:36 [ChrisL]
tal: mentioned that url at top of license, so should allow to have no text below. some foundries want just a link, no text.
15:32:06 [ChrisL]
ChrisL: please send that as a separate comment
15:32:57 [ChrisL]
Vlad: spec is clear that the text in a license element is about the license, not a copy of the license
15:33:54 [ChrisL]
... better to have some text, for users
15:35:09 [ChrisL]
tal: made some fonts for a foundry and they said that they wanted just a url, no text
15:36:17 [ChrisL]
... spec currently says we need both
15:36:26 [ChrisL]
... should it be either/or
15:36:46 [ChrisL]
ChrisL: seems more reasonable to me
15:37:20 [ChrisL]
Topic: test plan issues
15:37:40 [ChrisL]
tal: do we neeed null bytes. some things like that came up in the test plan, they are in red
15:38:28 [ChrisL]
15:39:25 [ChrisL]
tal: in the process of doing the test plan, multiple spec read-thoughs turned up some issues.
15:39:41 [ChrisL]
... some are clear, like the file has to be long enough to contain the header
15:40:08 [ChrisL]
... if the flavour is in contradiction with the actual table data. spec is silent on that.
15:40:42 [ChrisL]
ChrisL: there are multiple flavours for truetype
15:41:16 [ChrisL]
tal: thses have caused problems for text engines before
15:41:46 [ChrisL]
Vlad: packaging mechanism is separate - if you package a broken thing, the package is not at fault
15:41:59 [ChrisL]
tal: jdaggett said list them all, so i did
15:42:24 [ChrisL]
Vlad: think that particular one is out of scope
15:43:11 [ChrisL]
tal: its additional tests
15:43:37 [ChrisL]
Vlad: may cross boundary between packaging and font sanitising
15:45:14 [ChrisL]
ChrisL: these are good for a validator, but in spme cases its not the woff spec that is violated but the OT spec
15:45:29 [ChrisL]
tal: some t=of these are crashing bugs for certain OS
15:45:59 [ChrisL]
tal: number of tables, needs to be parseable
15:46:29 [ChrisL]
tal: some are tagged as format bit also need to be UA conformance as well
15:47:27 [ChrisL]
... read the wiki pages
15:48:22 [ChrisL]
Vlad: anything here needs more discussion?
15:48:31 [ChrisL]
tal: tried to be very clear
15:49:24 [ChrisL]
Vlad: lets discuss on email and make resolutions next week on the red items
15:49:32 [ChrisL]
15:49:53 [ChrisL]
tal: have worked on infrastructure for tests
15:50:26 [ChrisL]
... have been reading the css testsuite documentation
15:51:04 [ChrisL]
adjourned
15:51:11 [ChrisL]
zakim, list attendees
15:51:11 [Zakim]
As of this point the attendees have been Tal, ChrisL, +1.978.790.aaaa, Vlad
15:51:14 [ChrisL]
chair: vlad
15:52:18 [ChrisL]
(general appreciation for tal's work)
15:52:20 [ChrisL]
rrsagent, make minutes
15:52:20 [RRSAgent]
I have made the request to generate
ChrisL
15:52:27 [Zakim]
-Tal
15:52:28 [Zakim]
-tal.a
15:52:28 [Zakim]
-ChrisL
15:52:32 [tal]
tal has left #webfonts
15:52:33 [Zakim]
-Vlad
15:52:34 [Zakim]
IA_Fonts()10:00AM has ended
15:52:36 [Zakim]
Attendees were Tal, ChrisL, +1.978.790.aaaa, Vlad
18:00:26 [Zakim]
Zakim has left #webfonts | http://www.w3.org/2010/12/01-webfonts-irc | CC-MAIN-2014-10 | refinedweb | 1,250 | 67.42 |
im wrote a program to determine weather a triangle is scalene, isosceles or equilateral based on the given side lengths...its not working properly..i.e its giving isoceles when i enter data for an equilateral...etc etc... i fugured it was my logic in writing the program that was missing something....could anyone tell me how to tighten this up so that it works properly?
#include <stdio.h> main () { double side1, side2, side3 ; int abc; printf ("enter first side : "); scanf ("%lf", &side1); printf ("enter second side : "); scanf ("%lf", &side2); printf ("enter third side : "); scanf ("%lf", &side2); if ((side1 == side2)&&(side2 == side3)&&(side3 == side1)) printf ("Equilateral Triangle"); else if ((side1==side2)||(side2==side3)||(side3==side1)) printf ("Isosceles Triangle"); else if ((side1 != side2)&&(side2 != side3)&&(side3 !=side1)) printf ("Scalene Triangle"); scanf ("%d", &abc); return (0); }
the scanf at the end is to keep the program on the screen after it executes and displays the output..it usually does that (im using bloodshed's DevC++).
im guessing that there is something else i could put into the if statement's conditions, but im not sure at all... thanks in advance for your help | https://www.daniweb.com/programming/software-development/threads/405707/identifying-a-triangle | CC-MAIN-2018-13 | refinedweb | 191 | 70.84 |
Display images from cloneable fields is a common task for those who are building a website. For example, you may want to display a series of brand logos of typical clients or partners, even a testimonial section with an avatar along with the clients’ name and quote. In this series, we will take a ride to do it with a simple case study, brand logos.
If you are using Gutenberg, this part is for you. For other page builders, please wait for the upcoming tutorials.
Before Getting Started
We’ll need Meta Box and some of its extensions for this practice:
-;
- MB Views: it helps you to create templates as well as get and display fields’ values without touching the theme’s files.
You can install these extensions individually or use Meta Box AIO.
Video Version
Step 1: Create a Settings Page
Normally, we’ll create a Custom Post Type to create multiple posts for brands then each post is for a brand. But, today, I do a more convenient and simple way - creating a Settings Page. The information about all the brands will be input to that page. It means that all of them will be in one place only.
Now, go to Meta Box > Settings Page > Add New. In this case, the Settings Page is quite simple to contain the image of each brand, so just change the option name.
Now, a new menu named Brands appears. It’s my new Settings Page.
Step 2: Create Custom Fields for the Settings Page
In the Admin Dashboard, go to Meta Box > Custom Fields > Add New. I created fields with the below structure.
This is a group with three sub-fields inside. This group is. You can click Add more to add another brand’s information.
Now, let’s fill the information into the fields and move to the next step.
Step 3: Display Brands Information
To display the brand information, you normally must go to the theme’s files to add code or use a page builder. However, you have another way with Meta Box. We have the MB Views extension to create templates without touching the theme’s files.
Instead of typing code into the box in the Template tab, you can insert fields to get their data. And, in the previous tutorial, we used to create custom fields for posts, so we choose one from the Post tab. But, in this practice, we created custom fields for the Settings Page, so we go to the Site tab then find the custom fields that I created.
Because this group is cloneable so whenever you open the group here to find any field, it will auto-generate a Loop.
When inserting the fields, I also edit the code a little bit to create a rule for displaying images.
The first part is to set a rule that if there is no URL input to the URL field, the value from the Single Image field will be obtained and displayed.
When you insert the logo from the Single Image field, you can choose to size to output. Here I set it to be the thumbnail.
In the event that there is no input data in the Brand Logo Upload field, the image from the link in the URL field will be displayed.
If there is data in both the Image Upload and URL field, I set priority to display the image of the Brand Logo Upload field.
If you have any further information for the brand, such as the Brand Name I have in this case, remember to insert them in the next lines.
If you want to style this section, add some div tags. I also did it and here is all the code.
<div class="brand-group"> {% for clone in site.brands.brand_group %} <div class="brand-img"> {% if clone.brand_logo_url|trim is empty %} <img src="{{ clone.brand_logo_upload.thumbnail.url }}" width="{{ clone.brand_logo_upload.thumbnail.width }}" height="{{ clone.brand_logo_upload.thumbnail.height }}" alt="{{ clone.brand_logo_upload.thumbnail.alt }}"> {% elseif clone.brand_logo_upload.thumbnail.ID|trim is empty %} <img src="{{ clone.brand_logo_url }}"> {% else %} <img src="{{ clone.brand_logo_upload.thumbnail.url }}" width="{{ clone.brand_logo_upload.thumbnail.width }}" height="{{ clone.brand_logo_upload.thumbnail.height }}" alt="{{ clone.brand_logo_upload.thumbnail.alt }}"> {% endif %} <p class="name"> {{ clone.brand_name }} </p> </div> {% endfor %} </div>
To finish, move to the Settings section, choose the type of view as Shortcode.
After publishing this view, a shortcode will be generated automatically. You can copy and paste it to any page you want to display the template.
Now, you can see all of the brand logos along with their names displayed already.
You see that this section hasn’t looked good yet. Thus, we’ll need some JS and CSS to make it look better.
Step 4: Create Slider for the Brand Logos
As you see in the first image I put at the beginning of this post, the logos are in a slider, and brand names are displayed correspondingly. To have it, I’ll use some JS and CSS.
However, I’m using the My Custom Functionality plugin instead of adding them directly to the theme. Thanks to that, the slider won’t be affected when I change the theme. You can download this plugin from GitHub and install it on your website.
Download the JS and CSS Library
For the JS and CSS, I use the Slick library. It’s also available on Github. It includes several files, but we just need three of them.
Go to the folder of the My Custom Functionality plugin. Upload them into the corresponding JS and CSS folders.
Create Custom JS for Slider and Rules
Create a
custom.js file in the
JS folder, and add code.>' }); })
jQuery(".brand-group").slick({ }) is used to create a slider for the elements which have
.brand-group class.
Declare the JS and CSS Files
We need to declare all the JS and CSS files that we have just uploaded and created. I add images have already turned into a slider.
We still need to add some CSS to make it look better.
Step 5: Style the Slider using CSS
Traditionally, you have to add CSS to the Customizer or the theme’s files. But, with MB Views, you have a CSS tab for it.
All the CSS code is uploaded to Github, you can refer to it.
After adding CSS, my brand section turned into a new look.
Last Words
You see that displaying images from cloneable fields using Meta Box is not a difficult task. In my opinion, it’s very practical in some cases. We hope that this tutorial will help you to do it easier.
Remember to keep track of our channel for more upcoming tuts and feel free to leave a comment if you have any ideas or concerns.
Discussion (0) | https://practicaldev-herokuapp-com.global.ssl.fastly.net/wpmetabox/how-to-display-images-from-cloneable-fields-p1-with-gutenberg-4f2 | CC-MAIN-2022-27 | refinedweb | 1,132 | 74.79 |
Salesforce is the world’s best CRM service provider. They have higher than 40% business share in the Cloud CRM space and manages overall CRM scope with a market percentage of 19.7%. They were ranked the world’s #1 CRM for two following-to-back years and if the forecasted growth of Salesforce is anything to go by, the demand for experts with Salesforce training is only continuing to exponentially progress. This is everywhere Salesforce starts the design, and that is the reason to write a post on the popular frequently supplicated Salesforce interview questions.
Top 50 Salesforce Apex Interview Questions and Answers Pdf
Gratitude to the experience and wisdom accorded by some of our specialists from the industry, SVR Technologies have shortlisted the comprehensive list of the Top 50 Salesforce interview questions which in turn encourage you to breeze through your interview. Probably, this assists you to land a top-notch job in the field of your enthusiasm. In case you revisited a Salesforce interview freshly, we request you to post some questions that you have encountered. (Best Online Training Institute)
Here are the best 50 objective type sample Salesforce Interview questions and their answers are presented simply following them. Certain example questions are composed of professionals from SVR technologies who lead for Salesforce Admin training to give you an idea of a type of questions which may be claimed in an interview. We have acquired to provide accurate answers to all the questions.
1. What Is Apex?
Answer: It is the in-house technology of salesforce.com which is similar to Java programming with object-oriented concepts and to write our own custom logic.
- Apex is a procedural scripting language in discrete and executed by the Force.com platform.
- It runs natively on the Salesforce servers, making it more powerful and faster than non-server code, such as JavaScript/AJAX.
- It uses syntax that looks like Java.
- Apex can be written in triggers that act like database stored procedures.
- Apex allows developers to attach business logic to the record save process.
- It has built-in support for unit test creation and execution.
2. What are the advantages of using Batch Apex instead of a trigger?
Answer: A Batch class allows you to define a single job that can be broken up into manageable chunks that will be processed separately.
If you have 10,001 Account records in your org, this is impossible without some way of breaking it up.
3. What is Apex provides built-in support for common Force.com platform idioms and What Apex is including?
Answer:
- Data manipulation language (DML) calls, such as INSERT, UPDATE, and DELETE, that include built-in Dml Exception handling
- Inline Salesforce Object Query Language (SOQL) and Salesforce Object Search Language (SOSL) queries that return lists of subject
4. What is the difference between the public and global classes in Apex?
Answer:
- The public class can be accessed within the application or namespace. This is not exactly like a public modifier in Java.
- Global class visible everywhere, any application or namespace. Web Service must be declared as Global and which can be accessed inside JavaScript also. It is like a public modifier in Java.
5. What is Apex vs. Java: Commonalities?
Answer:
- Both have classes, inheritance, polymorphism, and other common OOP features.
- Both have the same name variable, expression, and looping syntax.
- Both have the same block and conditional statement syntax.
- Both use the same object, array, and comment notation.
- Both are compiled, strongly-typed, and transactional.
6. What is Apex Pages? Add Message?
Answer: Apex Pages. add Message Add a message to the current page context. Use Apex Pages to add and check for messages associated with the current page, as well as to reference the current page. In addition, Apex Pages is used as a namespace for the Page reference and Message classes.
7. What is Apex vs. Java: Differences?
Answer:
- Apex runs in a multi-tenant environment and is very controlled in its invocation and governor limits.
- To avoid confusion with case-insensitive SOQL queries, Apex is also case-insensitive.
- Apex is on-demand and is compiled and executed in the cloud.
- Apex is not a general-purpose programming language but is instead a proprietary language used for specific business logic functions.
- Apex requires unit testing for development into a production environment.
8. How Validation Rules Executed? Is It Page Layout / Visualforce Dependent?
Answer: The validation rules run at the data model level, so they are not affected by the UI. Any record that is saved in Salesforce will run through the validation rules.
9. Explain Considerations for Static keyword in Apex?
Answer:
- Apex classes cannot be static.
- Static allowed only in the outer class.
- Static variables not transferred as a part of View State.
- Static variables and static block run in the order in which they are written in class.
- Static variables are static only in the scope of a request.
10. What Is The Difference Between Database? insert And Insert?
Answer: Insert is the DML statement which is the same as database.insert.
However; database. insert gives more flexibility like rollback, default assignment rules, etc. We can achieve the database. insert behavior in insert by using the method setOptions.
Important Difference:
- If we use the DML statement(insert), then in bulk operation if an error occurs, the execution will stop and Apex code throws an error that can be handled in a try-catch block.
- If DML database methods(Database.insert) used, then if an error occurs the remaining records will be inserted/updated means partial DML operation will be done. Learn Salesforce Training Online From Real-Time Experts.
11. When do I want to export data into SF from Apex Data Loader, which Option should be enabled in Profile?
Answer: Enable API.
12. What Is The Scope Of Static Variable?
Answer:
-.
13. How To Write The “where” Clause In Soql When Group By Is Used?
Answer: We cannot use the “Where” clause with Group By instead we will need to use the “Having Clause“.
Example:
Get all the opportunity where more than one record exists with the same name and name contains “ABC”.
SELECT COUNT(Id) , Name FROM Opportunity GROUP BY Name Having COUNT(Id) > 1 AND Name like ‘%ABC%’
14. What Happens If Child Have Two Master Records And One Is Deleted?
Answer: Child records will be deleted.
15. Explain a few considerations for @Future annotation in Apex?
Answer:
- The method must be static
- Cannot return anything ( Only Void )
- To test @future methods, you should use startTest and stopTest to make it synchronous inside the Test class.
- A parameter to the @future method can only be primitive or a collection of the primitive data types.
- Cannot be used inside VF in Constructor, Set or Get methods.
- A @future method cannot call another @future method.
16. What Is Difference In Render, Rerender And Renderas Attributes Of Visualforce?
Answer:
- Render: It works like the “display” property of CSS. Used to show or hide the element.
- Rerender: After Ajax which component should be refreshed – available on command link, command button, action support, etc.
- Render as: render page as pdf, doc, and excel.
17. Explain Difference In Count() And Count(field name) In Soul?
Answer:.
18. How To Get The List Of All Available Subject In Salesforce Database Using Apex (dynamic Apex)?
Answer: Map<String, Schema.SObjectType> m = Schema.getGlobalDescribe();
19. What is batch apex? Why do we use batch apex?
Answer: A developer can now.
Batch Apex is exposed as an interface that must be implemented by the developer. Batch jobs can be programmatically invoked at runtime using Apex.
Batch Apex is exposed as an interface that must be implemented by the developer. Batch jobs can be programmatically invoked at runtime using Apex.
A need for Batch Apex: As you, all might know about the salesforce governor limits on its data. When you want to fetch thousands of records or fire DML on thousands of rows of objects it is very complex in salesforce and it does not allow you to operate on more than a certain number of records that satisfy the Governor limits.
But for medium to large enterprises, it is essential to manage thousands of records every day. Adding/editing/deleting them when needed.
Salesforce has come up with a powerful concept called Batch Apex. Batch Apex allows you to handle a number of records and manipulates them by using a specific syntax.
We have to create a global apex class which extends Database. Batch able Interface because of which the salesforce compiler will know, this class incorporates batch jobs. Below is a sample class that is designed to delete all the records of Account object (Let us say your organization contains more than 50 thousand records and you want to mass delete all of them).
20. How To Get All The Fields Of Subject Using Dynamic Apex?
Answer: Map<String, Schema.SObjectType> m = Schema.getGlobalDescribe() ;
Schema.SObjectType s = m.get(‘API_Name_Of_SObject’) ;
Schema.DescribeSObjectResult r = s.getDescribe() ;
Map<String, Schema.SObjectField> fields = r.fields.getMap();
21. members are declared in the Apex class. It has another advantage in the “number of lines of code” limit by salesforce which will drastically reduce
22. What are a few limitations of Savepoint or Transaction Control in Apex?
Answer:
- Each savepoint you set counts against the governor limit for DML statements.
- Static variables are not reverted during a rollback. If you try to run the trigger again, the static variables retain the values from the first run.
- Each rollback counts against the governor limit for DML statements. You will receive a Runtime error if you try to roll back the database additional times.
- The ID on an object inserted after setting a savepoint is not cleared after a rollback.
23. Explain The Need Or Importance Of The Controller Extension?
Answer: Controller extension is a very useful and important concept introduced by the salesforce recently. It gives the power to the programmer to extend the functionality of the existing custom controller or a standard controller.
A Visualforce can have a single Custom controller or standard controller but many controller extensions.
We can say that the custom extension is the supporter of a custom or it to that page only.
24. How To Force Lead Assignment Rule Via Apex While Updating Or Adding The Lead?
Answer: To enforce Assignment Rules in Apex you will need to perform the following steps:
- Instantiate the “Database.DMLOptions” class.
- Set the “use default rule” property of “assignmentRuleHeader” to True.
-);
25. How To Read The Parameter Value From The Url In Apex?
Answer: Consider that the parameter name is “RecordType”.
String record type = Apexpages.currentPage().getParameters().get(‘RecordType’);
26. What are the recommended ways to refactor in Apex?
Answer: I use the second method. After refactoring, I select the ‘src’ folder, use File Search/Replace and all the changes are made and saved to the server in one go.
27. If One Object In Salesforce Have 2 Triggers Which Runs “before Insert”. Is There Any Way To Control The Sequence Of Execution Of These Triggers?
Answer:Salesforce.com has documented that the trigger sequence cannot be predefined. As a best practice create one trigger per object and use comment blocks to separate different logic blocks. By having all logic in one trigger you may also be able to optimize on your SOQL queries.
28. What Is The Need Of “custom Controller” In Visualforce As Everything Can Be Done By The Combination Of Standard Controller + Extension Class?
Answer: Sharing setting is applied on standard object/extension by default; In case we don’t want to apply sharing setting in our code then Custom control
It is possible that the functionality of the page does not require any Standard object or may require more than one standard object, then, in that case, a Custom controller is required.
29. What Is The Difference Between Trigger?new And Trigger.old In Apex – Sfdc?
Answer:
Trigger.new:
- Returns a list of the new versions of the sObject records
- Note that this sObject list is only available in the insert and update triggers
- i.e., Trigger.new is available in before insert, after insert, before the update, and after update
- In Trigger.new records can only be modified before triggers.
Trigger.old:
- Returns a list of the old versions of the sObject records
- Note that this sObject list is only available in update and delete triggers.
- i.e., Trigger.old is available after insert, after update, before delete, and after the update.
30. Is there a defacto 3rd party utilities library for Apex such as Apache Commons is for Java?
Answer: Apex-lang is about as close to a Java-style library as you can get. It contains several strings, database, and collection utilities that mimmick Java functionality. Be aware though, some stuff including Comparing and Sorting collections is out of date with the advent of the Comparable interface in Apex. In addition to apex-lang, and like you suggest, I typically create or reuse static helper methods throughout my projects. Static helper methods are very convenient for reusing code in Chatter functionality, DML handling, Exception handling, Unit testing, etc.
31. How To Create Many To Many Relationships Between Object?
Answer:
- Creating Many to Many relationships in salesforce is a little tricky. You cannot create this type of relationship directly. Follow the below steps to create this type of relationship.
- Create both objects which should be interlinked.
- Create one custom object(also called junction object), which should have an auto number as unique identification and create two master relationships for both objects, no need to create a tab for this object.
- Now on both objects, add this field as a related list.
32. In Class Declaration If We Don’t Write Keyword “with Sharing” Then It Runs In System Mode Then Why Keyword “without Sharing” Is Introduced In Apex?
Answer: Let’s take an example, there is a class declared using “with sharing” and it calls the class method. ClassB is not declared with any keyword then by default “with sharing” will be applied to that class because the originating call is done through classA. To avoid this we have to explicitly define class with the keyword “without sharing”.
33. In Which Sequence Trigger And Automation Rules Run In Salesforce.com?
Answer: The following is the order salesforce logic is applied to a record.
- Old record loaded from database (or initialized for new inserts)
- New record values overwrite old values
- System Validation Rules
- All Apex “before” triggers (EE / UE only)
- Custom Validation Rules
- Record saved to the database (but not committed)
- Record reloaded from the database
- All Apex “after” triggers (EE / UE only)
- Assignment rules
- Auto-response rules
- Workflow rules
- Escalation rules
- Parent Rollup Summary Formula value updated (if present)
- Database commit
- Post-commit logic (sending email)
Additional notes: There is no way to control the order of execution within each group above.
34. What is the apex data loader?
Answer: Apex data loader is used to insert, update, upsert, export the data. By using the apex data loader we can import the data from outside the salesforce also.
35. What Is S-control?
Answer: S-Controls are the predominant salesforce.com widgets that are completely based on Javascript. These are hosted by salesforce but executed at the client-side. S-Controls are superseded by Visualforce now
36. If User Doesn’t Have Any Right On Particular Record And Have Only Read Level Access At Object Level. Can He Change The Record Owner?
Answer: Yes. In profile, there is the setting for “Transfer Record”.
37. Will Visual Force Still Supports The Merge Fields Usage Like S-control?
Answer: Just like S-Controls, Visualforce Pages support embedded merge fields, like the {!$User.FirstName} used in example.
38. In How Many Ways We Can Invoke The Apex Class?
Answer:
- Visualforce page
- Trigger
- Web Services
39. What Are Merge Fields? Explain With Example?
Answer: Merge fields are fields that we can put in Email templates, mail merge templates, custom link or formula fields to incorporate values from a record.
Example: {!CustomObject.FieldName__c}
40. In Which Scenario Share Object “mycustomobject__share” Is Not Available/created For Custom Object “my custom object” ?
Answer: The object’s organization-wide default access level must not be set to the most permissive access level. For custom Objects, that is Public Read/Write.
41..The scheduling method uses the user’s time zone for the basis of all schedules. You can only have 25 classes scheduled at one time.
Example Code:
String CRON_EXP = ‘0 0 * * * ?’;
clsScheduledHourly Sch = new clsScheduledHourly();
system.schedule(‘Hourly Sync’, CRON_EXP, sch);
42. What are the differences between static and non-static variables in Apex?
Answer: A static variable is associated with the class as a whole rather than with specific instances of a class. Non-static variables take on unique values with each object instance.
43. What Are The Types Of Controller In Visualforce?
Answer: There are basically two types of Controller in Visual force page:
- Standard Controller
- Custom Controller
44. Which SOQL statement can be used to get all records even from recycle bin or Achieved Activities?
Answer: We will need the “ALL Rows” clause of SOQL.
Sample : SELECT COUNT() FROM Contact WHERE AccountId = a.Id ALL ROWS
45. runes in a test method. The original system context is started again after all runs() test methods complete.
Example :
System.runAs(u) {
// The following code runs as user ‘u’
System.debug(‘Current User: ‘ + UserInfo.getUserName());
System.debug(‘Current Profile: ‘ + UserInfo.getProfileId()); }
// Run some code that checks record sharing
46. How can you lock record using SOQL so that it cannot be modified by another user?
Answer: we will need the “FOR UPDATE” clause of SOQL.
Sample : Account [] accts = [SELECT Id FROM Account LIMIT 2 FOR UPDATE];
47. Explain Test.setpage()?
Answer: It is used to set the context to the current page, normally used for testing the visual force controller.
48. If you set more than one savepoint, then roll back to a savepoint that is not the last savepoint you generated, What will happen to later savepoint variables?
Answer: If you generated savepoint SP1 first, savepoint SP2 after that, and then you rolled back to SP1, the variable SP2 would no longer be valid. You will receive a runtime error if you try to use it.
49. How To Round The Double To Two Decimal Places In Apex?
Answer: Decimal d = 100/3;
Double and = d.setScale(2);
50. What are a few Considerations about Trigger?
Answer:
- Upsert triggers to fire both before and after insert or before and after update triggers as appropriate.
- Merge triggers fire both before and after delete triggers for the losing records and before update triggers for the winning record only.
- Triggers that execute after a record has been undeleted only work with specific objects.
- Field history is not recorded until the end of a trigger. If you query field history in a trigger, you will not see any history for the current transaction.
- You can only use the Webservice keyword in a trigger when it is in a method defined as asynchronous; that is when the method is defined with the @future keyword.
- A trigger invoked by an insert, delete, or update of a recurring event or recurring task results in a runtime error when the trigger is called in bulk from the Force.com API.
- Merge trigger doesn’t fire there own trigger instead they fire delete and update of loosing and winning records respectively. | https://svrtechnologies.com/top-50-salesforce-apex-interview-questions-and-answers-pdf/ | CC-MAIN-2020-40 | refinedweb | 3,257 | 66.13 |
Each Answer to this Q is separated by one/two green lines.
I’m trying to struct a schema for db testing, and StructType apparently isn’t working for some reason. I’m following a tut, and it doesn’t import any extra module.
<type 'exceptions.NameError'>, NameError("name 'StructType' is not defined",), <traceback object at 0x2b555f0>)
I’m on spark 1.4.0, and Ubuntu 12 if that has anything to do with the problem. How would I fix this problem? Thank you in advance.
Did you import
StructType? If not
from pyspark.sql.types import StructType
should solve the problem.
from pyspark.sql.types import StructType
That would fix it but next you might get
NameError: name 'IntegerType' is not defined or
NameError: name 'StringType' is not defined ..
To avoid all of that just do:
from pyspark.sql.types import *
Alternatively import all the types you require one by one:
from pyspark.sql.types import StructType, IntegerType, StringType
All Types: Apache Spark Data Types
The answers/resolutions are collected from stackoverflow, are licensed under cc by-sa 2.5 , cc by-sa 3.0 and cc by-sa 4.0 .
| https://techstalking.com/programming/python/pyspark-structtype-is-not-defined/ | CC-MAIN-2022-40 | refinedweb | 192 | 69.38 |
NetBeans Selection Management Tutorial I-Using a TopComponent’s Lookup
Last reviewed on 2020-12-20
- Introduction to Selection
- Creating the NetBeans Platform Application Project
- Creating an API and Setting Up Dependencies
- Creating the Viewer Component
- Creating the Editor Component
- Running the Code
- So, What’s the Point?
- Changing Selected Objects on the Fly
- Providing More Than One Object
- Next Steps
This tutorial covers how to write components for the Apache NetBeans Platform that provide a "selected object" and how to write components that update themselves as the global selection changes. This is an important aspect of the application, and helps your component fit in with the behavior of other components.
For troubleshooting purposes, you are welcome to download the completed tutorial source code.
This tutorial is part 1 of a series. Part 2 builds on this tutorial to explain how to handle selection on a single item (such as one element in a tree view).
Introduction to later in this series.
Selection enables things such that other code is able to query. That bag of objects is its Lookup - essentially a Map where the keys are class objects and the values are objects that extend or implement the key-class. This is useful because it decouples the components that provide some object and the components that consume those objects so they can be implemented in separate modules, or new editors for existing objects can be provided without changing the rest of the system.
Creating the NetBeans Platform Application Project
The loosely-coupled modular example used in this tutorial will contain three modules constituting a NetBeans Platform application, as illustrated below:
Start by creating the NetBeans Platform application that will contain all three modules:
Choose Ctrl+Shift+N). Under Categories, expand Java with Ant, and select NetBeans Modules. Under Projects, select NetBeans Platform Application:(
Click Next.
In the Name and Location panel, type
EventManager set.
Choose Ctrl+Shift+N) again. If not already open, under Categories, expand Java with Ant, and select NetBeans Modules. Under Projects, select Module:(
Click Next.
In the Name and Location panel, type
MyAPI.
Click Next.
In the Basic Module Configuration panel, set the following values:
Code Name Base. The code name base is a string that uniquely identifies a module. By convention, the value of the code name base is the main package of the module. Therefore, if the main package of your module is going to be "org.me.foo", then that would normally also be the value of the code name base of the module. In this case, since the base package will be "org.myorg.myapi", set the code name base to
org.myorg.myapi. That will be the string used to identify the module by other modules that will need to make use of code within this module.
Module Display Name. Set the module display name to
My API. That is the text you will see displayed for the module in the Projects window in the IDE.
Localizing Bundle. Leave the location of the localizing bundle with the default value, so that localization keys/values will be stored in the main package, with the name
org/myorg/myapi.
Generate OSGi Bundle. Leave this unchecked to use the NetBeans module system. There are two module systems are supported by the NetBeans Platform, the NetBeans module system and the OSGi framework. You can use OSGi if required to meet your business requirements, although we use the NetBeans module system in this tutorial series.
The result should be as follows:
Click Finish.
Now create two more modules now, following step 3, 4, and 5 above. For the second module use "MyEditor" for the Project Name, with a Code Name Base of
org.myorg.myeditorand a Module Display Name of "My Editor". For the third module use "MyViewer" for the Project Name, with a Code Name Base of
org.myorg.myviewerand a Module Display Name of "My Viewer"..
Creating an API and Setting Up Dependencies
In this part of the tutorial, we that provides a unique identifier, and a date.
Right click the
org.myorg.myapipackage and choose New > Java Class.
Name the class
Event:
Click Finish.
Replace the default code with the following:
package org.myorg.myapi; import java.time.ZonedDateTime; public final class Event { private final ZonedDateTime date = ZonedDateTime.now(); private static int count = 0; private final int index; public Event() { index = count++; } public ZonedDateTime getDate() { return date; } public int getIndex() { return index; } @Override public String toString() { return index + " - " + date.toString(); } }
This will be all of the code that this module contains. As you can see, each time a new instance of
Event is created, a counter is incremented so there will be some unique identifier to each instance of
Event.
The next step is to have your API module export the
org.myorg.myapipackagein the Public Packages list, as shown below:
Click OK.
Now expand the Important Files node of the My API project. Open the Project Metadata file. On disk, this file is named
project.xml. Inside this file, notice the following section, which was added when you clicked OK in the dialog above:
class, so each of them needs to say that they depend on the API module. Right-click on the My Editor project node, and choose Properties. The Project Properties dialog will appear. Select the Libraries tab.
Click Add Dependency…
In the Filter text box, type
Event, which will refine the list of all available modules. Locate the "My API" module and select it:
Click OK to add the dependency.
You should see the following:
Click OK to close the Project Properties dialog.
When you open the Project Metadata file in the Important Files node of the My Editor.
Now add the same dependency for the My Viewer module, starting with right-click on the My Viewer project node and selecting Properties.
When this is done, the new contract between the modules is represented in the Project window as follows:
Creating the Viewer Component
Now you will create a singleton component that will track if there is an
Event available in the global selection (i.e., if the focused
TopComponent has one in its Lookup). If there is one, it will display some data about it. One common use case for this kind of functionality is creating master/detail views.
Generating a Singleton TopComponent
A "singleton component" is a component like the Projects window in the NetBeans IDE, or the Property Sheet or the Navigator - a component that there is only ever one of in the system. The Window New File dialog, select Module Development > Window, as shown below:
Click Next (or press Enter).
On the "Basic Settings" page of the wizard, select
exploreras the location in which to place your viewer component, and check the "Open on Application Start" checkbox to cause the window to open on startup, as shown below:
Click Next.
The "Name, Icon and Location" page of the wizard will appear. Set
MyVieweras the class name prefix:
Click Finish and you should see the following:
You now have a skeleton
TopComponent - a singleton component called
MyViewerTopComponent. The wizard created the Java class, and added the required module dependencies (under Libraries).
If not already open, double-click to open the
MyViewerTopComponentfile. Click its Source tab. Via the annotations that you can see at the top of the Java source file,
MyViewerTopComponentwill be registered in the layer file of the MyViewer module, together with an
Actionfor opening the
MyViewerTopComponentfrom the Window menu:
@ConvertAsProperties( dtd = "-//org.myorg.myviewer//MyViewer//EN", autostore = false ) @TopComponent.Description( preferredID = "MyViewerTopComponent", //iconBase="SET/PATH/TO/ICON/HERE"," ) @Messages({ "CTL_MyViewerAction=MyViewer", "CTL_MyViewerTopComponent=MyViewer Window", "HINT_MyViewerTopComponent=This is a MyViewer window" })
Creating a Context Sensitive TopComponent
Click its Design tab of the open
MyViewerTopComponent to access the "Matisse" GUI Builder (also known as the "form editor").
You will add two labels to the component, which will display some information about the selected
Event if there is one.
Drag two Labels (javax.swing.JLabel) to the form from the Palette (Ctrl+Shift+8), one below the other, as shown below:
Press F2 on the first label and then change the text as shown above, so that by default it displays "[Nothing selected]".
Click the Source button in the editor toolbar to switch to the code editor. Modify the signature of the class, so that
MyViewerTopComponentimplements
LookupListener:
public final class MyViewerTopComponent extends TopComponent implements LookupListener {
Right-click in the editor and choose Fix Imports, so that
LookupListener is imported.
Put the cursor over the lightbulb icon should appear in the editor margin. A popup hint should appear, as shown below:
Left click on the lightbulb icon in the editor margin, and when the popup appears, select the text "Implement all abstract methods".
You now have a class that implements
LookupListener (i.e. the
resultChanged method). Now it needs something to listen to..
Edit the source code of the
MyViewerTopComponentto add a lookup result member, and so that its
componentOpened,
componentClosed, and
resultChangedmethods are as follows:("[Nothing
Eventchanges, it will update the two `JLabel`s you put on the form..Lookup; import org.openide.util.LookupEvent; import org.openide.util.LookupListener; import org.openide.windows.TopComponent; import org.openide.util.NbBundle.Messages; import org.openide.util.Utilities;
Creating the Editor Component
Now you need something to actually provide instances of
Event for this viewer code to be of any use. Fortunately this is quite simple.
We will do this in the My Editor module, consistent with our goal of demonstrating loose coupling between the components of our application..
You will need to add four dependencies to the My Editor module for it to be able to find the classes you will be using.
Right click the My Editor project and choose Properties. On the Library page of the Project Properties dialog box, click the Add Dependency button, and type
TopComponent in the Filter textbox. The dialog should automatically suggest setting a dependency on the Window System API. Do the same thing for
Lookups (Lookup API). Also set a dependency on the Utilities API, Base Utilities API, and UI Utilities API, which provide various helpful supporting classes that are made available by the NetBeans Platform.
You should end up with six dependencies (the MyAPI dependency from the earlier part of this tutorial, plus the five you just added), as shown below:
You can also see these in the Libraries node of the My Editor project.
Right-click the
org.myorg.myeditorpackage in the My Editor project, and choose New > Other. When the New File dialog appears, select Swing GUI Forms from the Category selection, and JPanel Form from the File Types selection.
Click Next.
Set the class name to "MyEditor", and click:[Finish] to complete the wizard.
You should see
MyEditor.java open in with the Design view (form editor) open:
When the form editor opens, drop two Text Fields (javax.swing.JTextField) on the form, one above the other.
On the property sheet, set the "editable" property (checkbox) to
false for both text fields.
Click the Source button in the editor toolbar to switch to the code editor.
Change the signature of
MyEditorto extends
TopComponentinstead of
javax.swing.JPaneland annotate the class to specify the location of the window and the menu item for opening it:
=Open Editor"}) public class MyEditor extends TopComponent {
Add the following code to the constructor of
MyEditor, after the
initComponents()statement:.NbBundle;, which will be the subject of the next tutorial.
To make your editor component at least somewhat interesting (though it doesn’t actually edit anything), you set the text fields' values to values from the
Event, so you have something to display.
Running the Code
Now you’re ready to run the tutorial. Simply right click
EventManager, the application which contains your three modules, and choose Run from the popup menu. When the IDE opens, simply choose Window > Open Editor to invoke your action. Do this a couple of times, so that there are several of your editor components open. Your singleton
MyViewer window should also be open. Notice how the
MyViewer window’s contents change as you click different tabs, as shown here:
If you click in the Viewer window, or close all of the editor windows, note that the text changes to "[no selection]", as shown below:
So, What’s the Point?
So the key point of this tutorial is the way the code is split into three modules: the My Viewer module knows nothing about the My Editor module, and either one can run by itself. They only share a common dependency on My API. That means two things: 1. My Viewer and My Editor can be developed and shipped independently, and 2. Any module that wants to provide a different sort of editor than My Editor can do so, and the viewer component will work perfectly with it, as long as the replacement editor offers an instance of
Event from its Lookup.
To really picture the value of this, imagine
Event were something much more complex; imagine that
MyEditor is an image editor, and ` Event`.
Changing Selected Objects on the Fly
To make it really evident how powerful this approach can be, you’ll take one more step, and add a button to your editor component that lets it replace the
Event it has with a new one on the fly.
Open
MyEditorin the form editor (click the Design toolbar button in the editor toolbar), and drag a
Button(javax.swing.JButton) to it.
Set the
textproperty of the JButton to "Replace".
Right click the
JButtonand choose Events > Action > actionPerformed.
This will cause the code editor to open with the cursor in an event handler method. Make that method call
updateContent().
private void jButton1ActionPerformed(java.awt.event.ActionEvent evt) { updateContent(); }
Implement the missing method:
private void updateContent() { Event obj = new Event(); jTextField1.setText ("Event #" + obj.getIndex()); jTextField2.setText ("Created: " + obj.getDate()); setDisplayName ("MyEditor " + obj.getIndex()); content.set(Collections.singleton (obj), null); }
Note that this implementation is just the same as the lines that are in the constructor, except for the last one.
At the head of the class definition, add one final field:
public class MyEditor extends TopComponent { private final InstanceContent content = new InstanceContent();
InstanceContent is a class which allows us to modify the content of a Lookup (specifically an instance of
AbstractLookup) on the fly.
Remove the lines we added to the constructor earlier, except for the line beginning "associateLookup…". That line of the constructor should be changed as follows:
associateLookup (new AbstractLookup (content));
Add a call to
updateContent()to the constructor, after the
associateLookup()line.
updateContent();
Right-click in the editor and choose Fix Imports. The imports should now look like:
import java.util.Collections; import org.myorg.myapi.Event; import org.openide.awt.ActionID; import org.openide.awt.ActionReference; import org.openide.util.NbBundle; import org.openide.util.lookup.AbstractLookup; import org.openide.util.lookup.InstanceContent; import org.openide.windows.TopComponent;
You’re now ready to run the Event Manager again. Right click EventManager again and choose Run.
When you click the Replace button, all of the components update, including the instance of
MyViewer - everything.
Providing More Than One Object
This is all well and good for decoupling, but isn’t providing this one object from your component a bit like having a
Map that only contains one key and one value? The answer is, yes, it is like that. Where this technique becomes even more powerful is when you provide multiple objects from multiple APIs.
Event..
So the pattern in practice is to provide more than just a single object from your component’s
Lookup- different auxillary components and different actions will be interested in different aspects of the object being edited. These aspects can be cleanly separated into interfaces which those auxillary components and actions can depend on and listen for.
Next Steps
By now you may have noticed that some components have more granular selection logic, and even involve multiple selection. In the next tutorial you will cover how to use the Nodes API to handle that. | https://netbeans.apache.org/tutorials/nbm-selection-1.html | CC-MAIN-2021-17 | refinedweb | 2,677 | 55.84 |
The problem we will be considering is the solution of Laplace's problem with Neumann boundary conditions only:
\begin{eqnarray*} -\Delta u &=& f \qquad \mathrm{in}\ \Omega, \\ \partial_n u &=& g \qquad \mathrm{on}\ \partial\Omega. \end{eqnarray*}
It is well known that if this problem is to have a solution, then the forces need to satisfy the compatibility condition
\[ \int_\Omega f\; dx + \int_{\partial\Omega} g\; ds = 0. \]
We will consider the special case that \(\Omega\) is the circle of radius 1 around the origin, and \(f=-2\), \(g=1\). This choice satisfies the compatibility condition.
The compatibility condition allows a solution of the above equation, but it nevertheless retains an ambiguity: since only derivatives of the solution appear in the equations, the solution is only determined up to a constant. For this reason, we have to pose another condition for the numerical solution, which fixes this constant.
For this, there are various possibilities:
Fix one node of the discretization to zero or any other fixed value. This amounts to an additional condition \(u_h(x_0)=0\). Although this is common practice, it is not necessarily a good idea, since we know that the solutions of Laplace's equation are only in \(H^1\), which does not allow for the definition of point values because it is not a subset of the continuous functions. Therefore, even though fixing one node is allowed for discretized functions, it is not for continuous functions, and one can often see this in a resulting error spike at this point in the numerical solution.
Fixing the mean value over the domain to zero or any other value. This is allowed on the continuous level, since \(H^1(\Omega)\subset L^1(\Omega)\) by Sobolev's inequality, and thus also on the discrete level since we there only consider subsets of \(H^1\).
We will choose the last possibility, since we want to demonstrate another technique with it.
While this describes the problem to be solved, we still have to figure out how to implement it. Basically, except for the additional mean value constraint, we have solved this problem several times, using Dirichlet boundary values, and we only need to drop the treatment of Dirichlet boundary nodes. The use of higher order mappings is also rather trivial and will be explained at the various places where we use it; in almost all conceivable cases, you will only consider the objects describing mappings as a black box which you need not worry about, because their only uses seem to be to be passed to places deep inside the library where functions know how to handle them (i.e. in the
FEValues classes and their descendants).
The tricky point in this program is the use of the mean value constraint. Fortunately, there is a class in the library which knows how to handle such constraints, and we have used it quite often already, without mentioning its generality. Note that if we assume that the boundary nodes are spaced equally along the boundary, then the mean value constraint
\[ \int_{\partial \Omega} u(x) \; ds = 0 \]
can be written as
\[ \sum_{i\in\partial\Omega_h} u_i = 0, \]
where the sum shall run over all degree of freedom indices which are located on the boundary of the computational domain. Let us denote by \(i_0\) that index on the boundary with the lowest number (or any other conveniently chosen index), then the constraint can also be represented by
\[ u_{i_0} = \sum_{i\in\partial\Omega_h\backslash i_0} -u_i. \]
This, luckily, is exactly the form of constraints for which the ConstraintMatrix class was designed. Note that we have used this class in several previous examples for the representation of hanging nodes constraints, which also have this form: there, the middle vertex shall have the mean of the values of the adjacent vertices. In general, the ConstraintMatrix class is designed to handle homogeneous constraints of the form
\[ CU = 0 \]
where \(C\) denotes a matrix, and \(U\) the vector of nodal values.
In this example, the mean value along the boundary allows just such a representation, with \(C\) being a matrix with just one row (i.e. there is only one constraint). In the implementation, we will create a ConstraintMatrix object, add one constraint (i.e. add another row to the matrix) referring to the first boundary node \(i_0\), and insert the weights with which all the other nodes contribute, which in this example happens to be just \(-1\).
Later, we will use this object to eliminate the first boundary node from the linear system of equations, reducing it to one which has a solution without the ambiguity of the constant shift value. One of the problems of the implementation will be that the explicit elimination of this node results in a number of additional elements in the matrix, of which we do not know in advance where they are located and how many additional entries will be in each of the rows of the matrix. We will show how we can use an intermediate object to work around this problem.
But now on to the implementation of the program solving this problem...
As usual, the program starts with a rather long list of include files which you are probably already used to by now:
Just this one is new: it declares a class DynamicSparsityPattern, which we will use and explain further down below.
We will make use of the std::find algorithm of the C++ standard library, so we have to include the following file for its declaration:
The last step is as in all previous programs:
Then we declare a class which represents the solution of a Laplace problem. As this example program is based on step-5, the class looks rather the same, with the sole structural difference that the functions
assemble_system now calls
solve itself, and is thus called
assemble_and_solve, and that the output function was dropped since the solution function is so boring that it is not worth being viewed.
The only other noteworthy change is that the constructor takes a value representing the polynomial degree of the mapping to be used later on, and that it has another member variable representing exactly this mapping. In general, this variable will occur in real applications at the same places where the finite element is declared or used.
Construct such an object, by initializing the variables. Here, we use linear finite elements (the argument to the
fe variable denotes the polynomial degree), and mappings of given order. Print to screen what we are about to do.
The first task is to set up the variables for this problem. This includes generating a valid
DoFHandler object, as well as the sparsity patterns for the matrix, and the object representing the constraints that the mean value of the degrees of freedom on the boundary be zero.
The first task is trivial: generate an enumeration of the degrees of freedom, and initialize solution and right hand side vector to their correct sizes:
Next task is to construct the object representing the constraint that the mean value of the degrees of freedom on the boundary shall be zero. For this, we first want a list of those nodes which are actually at the boundary. The
DoFTools namespace has a function that returns an array of Boolean values where
true indicates that the node is at the boundary. The second argument denotes a mask selecting which components of vector valued finite elements we want to be considered. This sort of information is encoded using the ComponentMask class (see also GlossComponentMask). Since we have a scalar finite element anyway, this mask in reality should have only one entry with a
true value. However, the ComponentMask class has semantics that allow it to represents a mask of indefinite size whose every element equals
true when one just default constructs such an object, so this is what we'll do here.
Now first for the generation of the constraints: as mentioned in the introduction, we constrain one of the nodes on the boundary by the values of all other DoFs on the boundary. So, let us first pick out the first boundary node from this list. We do that by searching for the first
true value in the array (note that
std::find returns an iterator to this element), and computing its distance to the overall first element in the array to get its index:
Then generate a constraints object with just this one constraint. First clear all previous content (which might reside there from the previous computation on a once coarser grid), then add this one line constraining the
first_boundary_dof to the sum of other boundary DoFs each with weight -1. Finally, close the constraints object, i.e. do some internal bookkeeping on it for faster processing of what is to come later:
Next task is to generate a sparsity pattern. This is indeed a tricky task here. Usually, we just call
DoFTools::make_sparsity_pattern and condense the result using the hanging node constraints. We have no hanging node constraints here (since we only refine globally in this example), but we have this global constraint on the boundary. This poses one severe problem in this context: the
SparsityPattern class wants us to state beforehand the maximal number of entries per row, either for all rows or for each row separately. There are functions in the library which can tell you this number in case you just have hanging node constraints (namely
DoFHandler::max_coupling_between_dofs), but how is this for the present case? The difficulty arises because the elimination of the constrained degree of freedom requires a number of additional entries in the matrix at places that are not so simple to determine. We would therefore have a problem had we to give a maximal number of entries per row here.
Since this can be so difficult that no reasonable answer can be given that allows allocation of only a reasonable amount of memory, there is a class DynamicSparsityPattern, that can help us out here. It does not require that we know in advance how many entries rows could have, but allows just about any length. It is thus significantly more flexible in case you do not have good estimates of row lengths, however at the price that building up such a pattern is also significantly more expensive than building up a pattern for which you had information in advance. Nevertheless, as we have no other choice here, we'll just build such an object by initializing it with the dimensions of the matrix and calling another function
DoFTools::make_sparsity_pattern to get the sparsity pattern due to the differential operator, then condense it with the constraints object which adds those positions in the sparsity pattern that are required for the elimination of the constraint.
Finally, once we have the full pattern, we can initialize an object of type
SparsityPattern from it and in turn initialize the matrix with it. Note that this is actually necessary, since the DynamicSparsityPattern is so inefficient compared to the
SparsityPattern class due to the more flexible data structures it has to use, that we can impossibly base the sparse matrix class on it, but rather need an object of type
SparsityPattern, which we generate by copying from the intermediate object.
As a further sidenote, you will notice that we do not explicitly have to
compress the sparsity pattern here. This, of course, is due to the fact that the
copy_from function generates a compressed object right from the start, to which you cannot add new entries anymore. The
compress call is therefore implicit in the
copy_from call.
The next function then assembles the linear system of equations, solves it, and evaluates the solution. This then makes three actions, and we will put them into eight true statements (excluding declaration of variables, and handling of temporary vectors). Thus, this function is something for the very lazy. Nevertheless, the functions called are rather powerful, and through them this function uses a good deal of the whole library. But let's look at each of the steps.
First, we have to assemble the matrix and the right hand side. In all previous examples, we have investigated various ways how to do this manually. However, since the Laplace matrix and simple right hand sides appear so frequently in applications, the library provides functions for actually doing this for you, i.e. they perform the loop over all cells, setting up the local matrices and vectors, and putting them together for the end result.
The following are the two most commonly used ones: creation of the Laplace matrix and creation of a right hand side vector from body or boundary forces. They take the mapping object, the
DoFHandler object representing the degrees of freedom and the finite element in use, a quadrature formula to be used, and the output object. The function that creates a right hand side vector also has to take a function object describing the (continuous) right hand side function.
Let us look at the way the matrix and body forces are integrated:
That's quite simple, right?
Two remarks are in order, though: First, these functions are used in a lot of contexts. Maybe you want to create a Laplace or mass matrix for a vector values finite element; or you want to use the default Q1 mapping; or you want to assembled the matrix with a coefficient in the Laplace operator. For this reason, there are quite a large number of variants of these functions in the
MatrixCreator and
MatrixTools namespaces. Whenever you need a slightly different version of these functions than the ones called above, it is certainly worthwhile to take a look at the documentation and to check whether something fits your needs.
The second remark concerns the quadrature formula we use: we want to integrate over bilinear shape functions, so we know that we have to use at least a Gauss2 quadrature formula. On the other hand, we want to have the quadrature rule to have at least the order of the boundary approximation. Since the order of Gauss-r is 2r, and the order of the boundary approximation using polynomials of degree p is p+1, we know that 2r>=p+1. Since r has to be an integer and (as mentioned above) has to be at least 2, this makes up for the formula above computing
gauss_degree.
Since the generation of the body force contributions to the right hand side vector was so simple, we do that all over again for the boundary forces as well: allocate a vector of the right size and call the right function. The boundary function has constant values, so we can generate an object from the library on the fly, and we use the same quadrature formula as above, but this time of lower dimension since we integrate over faces now instead of cells:
Then add the contributions from the boundary to those from the interior of the domain:
For assembling the right hand side, we had to use two different vector objects, and later add them together. The reason we had to do so is that the
VectorTools::create_right_hand_side and
VectorTools::create_boundary_right_hand_side functions first clear the output vector, rather than adding up their results to previous contents. This can reasonably be called a design flaw in the library made in its infancy, but unfortunately things are as they are for some time now and it is difficult to change such things that silently break existing code, so we have to live with that.
Now, the linear system is set up, so we can eliminate the one degree of freedom which we constrained to the other DoFs on the boundary for the mean value constraint from matrix and right hand side vector, and solve the system. After that, distribute the constraints again, which in this case means setting the constrained degree of freedom to its proper value
Finally, evaluate what we got as solution. As stated in the introduction, we are interested in the H1 semi-norm of the solution. Here, as well, we have a function in the library that does this, although in a slightly non-obvious way: the
VectorTools::integrate_difference function integrates the norm of the difference between a finite element function and a continuous function. If we therefore want the norm of a finite element field, we just put the continuous function to zero. Note that this function, just as so many other ones in the library as well, has at least two versions, one which takes a mapping as argument (which we make us of here), and the one which we have used in previous examples which implicitly uses
MappingQ1. Also note that we take a quadrature formula of one degree higher, in order to avoid superconvergence effects where the solution happens to be especially close to the exact solution at certain points (we don't know whether this might be the case here, but there are cases known of this, and we just want to make sure):
Then, the function just called returns its results as a vector of values each of which denotes the norm on one cell. To get the global norm, a simple computation shows that we have to take the l2 norm of the vector:
Last task – generate output:
The following function solving the linear system of equations is copied from step-5 and is explained there in some detail:
Finally the main function controlling the different steps to be performed. Its content is rather straightforward, generating a triangulation of a circle, associating a boundary to it, and then doing several cycles on subsequently finer grids. Note again that we have put mesh refinement into the loop header; this may be something for a test program, but for real applications you should consider that this implies that the mesh is refined after the loop is executed the last time since the increment clause (the last part of the three-parted loop header) is executed before the comparison part (the second one), which may be rather costly if the mesh is already quite refined. In that case, you should arrange code such that the mesh is not further refined after the last loop run (or you should do it at the beginning of each run except for the first one).
After all the data is generated, write a table of results to the screen:
Finally the main function. It's structure is the same as that used in several of the previous examples, so probably needs no more explanation.
This is the main loop, doing the computations with mappings of linear through cubic mappings. Note that since we need the object of type
LaplaceProblem<2> only once, we do not even name it, but create an unnamed such object and call the
run function of it, subsequent to which it is immediately destroyed again.
This is what the program outputs:
As we expected, the convergence order for each of the different mappings is clearly quadratic in the mesh size. What is interesting, though, is that the error for a bilinear mapping (i.e. degree 1) is more than three times larger than that for the higher order mappings; it is therefore clearly advantageous in this case to use a higher order mapping, not because it improves the order of convergence but just to reduce the constant before the convergence order. On the other hand, using a cubic mapping only improves the result further insignificantly, except for the case of very coarse grids. | https://www.dealii.org/8.4.1/doxygen/deal.II/step_11.html | CC-MAIN-2019-39 | refinedweb | 3,265 | 51.72 |
We create a Web Form in Visual Studio, a .cs file means code
file class is automatically create. That .cs file means class has default
usings for namespace.
using System;using System.Collections.Generic;using System.Linq;using System.Web;using System.Web.UI;using System.Web.UI.WebControls;
But generally we don't use all namespaces in that class so we want remove unused
namespaces from file. We can remove
namespace manually but it takes time and need full knowledge of class
library so we can use Visual Studio .
Step 1: Right Click
in .cs File.
Step 2: Move on
Organize usings.
Step 3: Click on Remove Unused Usings.
After
that we have only those namespaces in the file these are using. | http://www.c-sharpcorner.com/blogs/remove-unused-usings-from-a-class1 | CC-MAIN-2017-34 | refinedweb | 123 | 60.51 |
Java's basic output class is java.io.OutputStream :
public abstract class OutputStream
This class provides the fundamental methods needed to write data. These are:
public abstract void write(int b) throws IOException public void write(byte[] data) throws IOException public void write(byte[] data, int offset, int length) throws IOException public void flush( ) throws IOException public void close( ) throws IOException
Subclasses of OutputStream use these methods to write data onto particular media. For instance, a FileOutputStream uses these methods to write data into a file. A TelnetOutputStream uses these methods to write data onto a network connection. A ByteArrayOutputStream uses these methods to write data into an expandable byte array. But whichever medium you're writing to, you mostly use only these same five methods. Sometimes you may not even know exactly what kind of stream you're writing onto. For instance, you won't find TelnetOutputStream in the Java class library documentation. It's deliberately hidden inside the sun packages. It's returned by various methods in various classes in java.net , like the getOutputStream() method of java.net.Socket . However, these methods are declared to return only OutputStream , not the more specific subclass TelnetOutputStream . That's the power of polymorphism. If you know how to use the superclass, you know how to use all the subclasses, too.
OutputStream 's fundamental method is write(int b) . This method takes an integer from 0 to 255 as an argument and writes the corresponding byte to the output stream. This method is declared abstract because subclasses need to change it to handle their particular medium. For instance, a ByteArrayOutputStream can implement this method with pure Java code that copies the byte into its array. However, a FileOutputStream will need to use native code that understands how to write data in files on the host platform.
Take note that although this method takes an int as an argument, it actually writes an unsigned byte. Java doesn't have an unsigned byte data type, so an int has to be used here instead. The only real difference between an unsigned byte and a signed byte is the interpretation. They're both made up of eight bits, and when you write an int onto a network connection using write(int b) , only eight bits are placed on the wire. If an int outside the range 0-255 is passed to write(int b) , the least significant byte of the number is written and the remaining three bytes are ignored. (This is the effect of casting an int to a byte .) On rare occasions, however, you may find a buggy third-party class that does something different, such as throwing an IllegalArgumentException or always writing 255, so it's best not to rely on this behavior, if possible.
For example, the character generator protocol defines a server that sends out ASCII text. The most popular variation of this protocol sends 72-character lines containing printable ASCII characters. (The printable ASCII characters are those between 33 and 126 inclusive that exclude the various whitespace and control characters.) The first line contains characters 33 through 104, sorted. The second line contains characters 34 through 105. The third line contains characters 35 through 106. This continues through line 29, which contains characters 55 through 126. At that point, the characters wrap around so that line 30 contains characters 56 through 126 followed by character 33 again. Lines are terminated with a carriage return (ASCII 13) and a linefeed (ASCII 10). The output looks like this:
!"#$%&'( )*+,-. %&'( )*+,-./0123456789:;<=>?@ABCDEFGHIJKLMNOPQRSTUVWXYZ[\]^_`abcdefghijkl &'( )*+,-./0123456789:;<=>?@ABCDEFGHIJKLMNOPQRSTUVWXYZ[\]^_`abcdefghijklm '( )*+,-./0123456789:;<=>?@ABCDEFGHIJKLMNOPQRSTUVWXYZ[\]^_`abcdefghijklmn
Since ASCII is a 7-bit character set, each character is sent as a single byte. Consequently, this protocol is straightforward to implement using the basic write( ) methods, as the next code fragment demonstrates :
public static void generateCharacters(OutputStream out) throws IOException { int firstPrintableCharacter = 33; int numberOfPrintableCharacters = 94; int numberOfCharactersPerLine = 72; int start = firstPrintableCharacter; while (true) { /* infinite loop */ for (int i = start; i < start+numberOfCharactersPerLine; i++) { out.write(( (i-firstPrintableCharacter) % numberOfPrintableCharacters) + firstPrintableCharacter); } out.write('\r'); // carriage return out.write('\n'); // linefeed start = ((start+1) - firstPrintableCharacter) % numberOfPrintableCharacters + firstPrintableCharacter; }
The character generator server class (the exact details of which will have to wait until we discuss server sockets in Chapter 10) passes an OutputStream named out to the generateCharacters( ) method. Bytes are written onto out one at a time. These bytes are given as integers in a rotating sequence from 33 to 126. Most of the arithmetic here is to make the loop rotate in that range. After each 72 character chunk is written, a carriage return and a linefeed are written onto the output stream. The next start character is calculated and the loop repeats. The entire method is declared to throw IOException . That's important because the character generator server will terminate only when the client closes the connection. The Java code will see this as an IOException .
Writing a single byte at a time is often inefficient. For example, every TCP segment that goes out your Ethernet card contains at least 40 bytes of overhead for routing and error correction. If each byte is sent by itself, you may be stuffing the network with 41 times more data than you think you are! Consequently, most TCP/IP implementations buffer data to some extent. That is, they accumulate bytes in memory and send them to their eventual destination only when a certain number have accumulated or a certain amount of time has passed. However, if you have more than one byte ready to go, it's not a bad idea to send them all at once. Using write(byte[] data) or write(byte[] data, int offset, int length) is normally much faster than writing all the components of the data array one at a time. For instance, here's an implementation of the generateCharacters() method that sends a line at a time by packing a complete line into a byte array:
public static void generateCharacters(OutputStream out) throws IOException { int firstPrintableCharacter = 33; int numberOfPrintableCharacters = 94; int numberOfCharactersPerLine = 72; int start = firstPrintableCharacter; byte[] line = new byte[numberOfCharactersPerLine+2]; // the +2 is for the carriage return and linefeed while (true) { /* infinite loop */ for (int i = start; i < start+numberOfCharactersPerLine; i++) { line[i-start] = (byte) ((i-firstPrintableCharacter) % numberOfPrintableCharacters + firstPrintableCharacter); } line[72] = (byte) '\r'; // carriage return line[73] = (byte) '\n'; // line feed out.write(line); start = ((start+1)-firstPrintableCharacter) % numberOfPrintableCharacters + firstPrintableCharacter; } }
The algorithm for calculating which bytes to write when is the same as for the previous implementation. The crucial difference is that the bytes are packed into a byte array before being written onto the network. Also, notice that the int result of the calculation must be cast to a byte before being stored in the array. This wasn't necessary in the previous implementation because the single byte write() method is declared to take an int as an argument.
Streams can also be buffered in software, directly in the Java code as well as in the network hardware. Typically, this is accomplished by chaining a BufferedOutputStream or a BufferedWriter to the underlying stream, a technique we'll explore shortly. Consequently, if you are done writing data, it's important to flush the output stream. For example, suppose you've written a 300-byte request to an HTTP 1.1 server that uses HTTP Keep-Alive. You generally want to wait for a response before sending any more data. However, if the output stream has a 1,024-byte buffer, the stream may be waiting for more data to arrive before it sends the data out of its buffer. No more data will be written onto the stream until the server response arrives, but the response is never going to arrive because the request hasn't been sent yet! The buffered stream won't send the data to the server until it gets more data from the underlying stream, but the underlying stream won't send more data until it gets data from the server, which won't send data until it gets the data that's stuck in the buffer! Figure 4-1 illustrates this Catch-22. The flush() method breaks the deadlock by forcing the buffered stream to send its data even if the buffer isn't yet full.
It's important to flush your streams whether you think you need to or not. Depending on how you got hold of a reference to the stream, you may or may not know whether it's buffered. (For instance, System.out is buffered whether you want it to be or not.) If flushing isn't necessary for a particular stream, it's a very low cost operation. However, if it is necessary, it's very necessary. Failing to flush when you need to can lead to unpredictable, unrepeatable program hangs that are extremely hard to diagnose if you don't have a good idea of what the problem is in the first place. As a corollary to all this, you should flush all streams immediately before you close them. Otherwise, data left in the buffer when the stream is closed may get lost.
Finally, when you're done with a stream, close it by invoking its close( ) method. This releases any resources associated with the stream, such as file handles or ports. Once an output stream has been closed, further writes to it throw IOException s. However, some kinds of streams may still allow you to do things with the object. For instance, a closed ByteArrayOutputStream can still be converted to an actual byte array and a closed DigestOutputStream can still return its digest. | https://flylib.com/books/en/1.135.1.33/1/ | CC-MAIN-2021-31 | refinedweb | 1,602 | 53.81 |
i-Names Pick Up Steam 158
There's been coverage in LJ on the whole "Identity Commons idea. Basically, it's a domain registrar for your unique name - with them on sale already. ASN has published a whitepaper on the topic as well.
When Dexter's on the Internet, can Hell be far behind?"
What about XNS names? (Score:3, Interesting)
Re:What about XNS names? (Score:5, Insightful)
anyways, maybe they sold lifetime subs to their previous thing.
now they sell "As a critical part of its mission Identity Commons is offering a time-limited opportunity for individuals to register a global i-name (opens new window) for 50 years for only $25 USD.".
so.. is it going to cost more after this limited time? with all the referral shit too it's starting to sound too much like a network marketing semi-scam - with "pay now, the product may be very good in the future! you can't afford to stay away!" attitude.
Re:What about XNS names? (Score:1)
Hmm. And what happens if this catches on and domain name piracy spreads to real name piracy? (That's a joke, son - we already have identity theft for that. Although I wonder how many Joseph Smiths there are out there, for example.)
How unique are names anyway?
Re:What about XNS names? (Score:1, Insightful)
Nah, what they aren't telling you is that in 5 years they'll start a new single-sign-in project and call it TheID or something, and all the websites will start using that, forcing you to shell out another $25 for a 50 year TheID account.
Re:What about XNS names? (Score:4, Insightful)
The whole think reeks of a profit machine.
if anyone really wants to wast $25, donate it to Mozilla [mozilla.org].
Re:What about XNS names? (Score:2, Insightful)
Re:What about XNS names? (Score:2)
BTW, I've got some twj-names for $24 if you want to save a buck. And for a century!!!
I visited the site but couldn't figure out what it was besides "gimme $25" so gave up after 30 seconds.
Re:What about XNS names? (Score:2, Informative)
Answer 50 years. BTW, THIS IS TRUSTED COMPUTING! (Score:5, Interesting)
From the FAQ: In this program, individuals may purchase a 50-year global personal i-name [2idi.com] What isn't in the FAQ is that you are only reserving the name for 50 years and getting 2 years of free "managment services". After that management fees are around $10 a year.
Now that I have answered your question and justified leeching off of the first high rated post (chuckle) I have an important message:
IT IS A FRONT FOR TRUSTED COMPUTING AND DRM!!
IT IS A FRONT FOR TRUSTED COMPUTING AND DRM!!
IT IS A FRONT FOR TRUSTED COMPUTING AND DRM!!
The organisations involved, OASIS (oasis-open.org), XDI.ORG and the others, they are all TRUSTED COMPUTING groups creating "open standards" for ENFORCING DRIGITAL RIGHTS MANAGAMENT systems.
One of OASIS's primary projects is:
Extensible Rights Markup Language (XrML): 'The Digital Rights Language for Trusted Content and Services'.
XDI.org's FAQ
What does XDI.ORG do.
EFF on Trusted Computing [eff.org]
GNU.org on Trusted Computing [gnu.org]
Wikipedia on Trusted Computing [wikipedia.org]
-
Re:Answer 50 years. BTW, THIS IS TRUSTED COMPUTIN (Score:2)
What is the basis for this? Are you saying I won't be able to write any programs on my own?
Re:Answer 50 years. BTW, THIS IS TRUSTED COMPUTIN (Score:2)
You can do that just fine for programs YOU wrote, or "normal" programs which other people wrote. The problem kicks in when someone intentionally utilizes the Trust system. For example the RIAA can give you a GPL open source DRM enforcing music player. You could even compile it yourself (you'd have to get teh EXE exactly right) and it will play the music files just fine and it will enforce the DRM. If you attempt to modify that program in any w
Re:Answer 50 years. BTW, THIS IS TRUSTED COMPUTIN (Score:2)
The problem is that in a "Trusted Computing" environment, you won't be able to run your own program without the encryption keys. The problem now becomes getting said keys. Also, the "secure storage" part of it, which is touted to protect your private data from malicious crackers and malware, keys in files to the program they were run in. For example- if you created a file in vim in a TrustedLinux distro, you wouldn't be able to do anything with that file except in vim. That is, if you can even run vim.
Re:Answer 50 years. BTW, THIS IS TRUSTED COMPUTIN (Score:3, Insightful)
Technically Oasis projects are designed to be "platfrom independant". If you actually look at the projects Oasis is working on they all revolve around DRM and DRM support systems. In particular a central project is site: "eXtensible rights Markup Language" [google.com], which is a general language for DRM enforment.
If you read the technical specifications of their various projects, including XrML, which I did several months ago, they sta
Re:What about XNS names? (Score:2)
Well.. (Score:4, Funny)
Re:Well.. (Score:3, Interesting)
Re:Well.. (Score:1).
Here's what I got when I typed in my desired i-name:
Your new gl
Re:Well.. (Score:2)
They suggest you use only one for all your i-names (e.g. "=beatdown" and "=Brown.Dwarf")
(not a putdown but an attempt to educate readers)
Ahhhh! (Score:4, Funny)
UNTERMINATED STRING CONSTANT. My head hurts now
With something as clumsy as '=victor.grey' (Score:3, Insightful)
Re:With something as clumsy as '=victor.grey' (Score:2)
Those "guys" would be, I believe, one Vint Cerf [mci.com].
Re:With something as clumsy as '=victor.grey' (Score:2)
25$ for 50 years ? (Score:4, Informative)
Re:25$ for 50 years ? (Score:2)
Should that become
foo.van.der.bar ?
How do you dilineate first name from surnage ?
In the case of
foo.van.der.bar foo is the first name, and the last 3 parts are the last name
With
st.john.bar, St John is the first name
If it's going to be global, and it's going to be useful, surely there should be some way of identifying these parts of a name ?
Re:25$ for 50 years ? (Score:3, Informative)
note that I neither affirm nor condem this "i name" business, just noting that the "i name" is not even designed to be parsed into a real name, so your points about "St. Joh
Re:25$ for 50 years ? (Score:1, Funny)
=porn is still available
You're welcome.
Poor site (Score:2)
I had a quick skim of the site and I'm still none the wiser.
Re:Poor site (Score:1)
$25 for 50 years - provided they dont go 'belly up' aka chapter 11 or whatever its called where you come from.
Re:Poor site (Score:5, Insightful)
you know why it's wordy and techie? to get techies to jump in quick to register their own name(s). you're not supposed to stop and think for a second if that 25$ is a ripoff or not. the whole community 'feel'(non mega polished with flash) in it is just intended to hide what's underneath.
it's techy and named so 'commons' so that you wouldn't first think that it's a firm that's taking twenty five bucks for you to register a crappy name on it, with basically no real usage on anywhere at all!
Re:Poor site (Score:2)
How Come? (Score:4, Insightful)
Re:How Come? (Score:1)
Re:How Come? (Score:2)
Re:How Come? (Score:2, Funny)
Re:How Come? (Score:2)
Re:How Come? (Score:2)
Re:How Come? (Score:2)
That's the sound of that answer going right over my head. K, thx!
Re:How Come? (Score:2, Insightful)
You're on Slashdot, do you even have to ask? Microsoft could donate $1 billion to cancer research and people here would still find a way to make it seem evil.
Re:How Come? (Score:2)
Re:How Come? (Score:2)
You're surely a troll, but:
WTF? Would you make the same argument for microscopes, textbooks, or PhD-holding faculty?
Just because they would never be able to afford it does not make it any less of a charitable donation.
Re:How Come? (Score:2)
Because... (Score:5, Insightful)
A hopefully open consortium of people doing universal identity (not saying this idea is necessarily it) would be doing it for the public good, not for greed or a mechanism to use a monopoly position to force its products on people.
Good Reasons... (Score:2, Interesting)
Re:Because... (Score:2)
Re:How Come? (Score:4, Informative)
The motivations for each group are entirely different. Go and listen to Owen Davis' speach here. [itconversations.com]
Re:How Come? (Score:2, Insightful)
Because the Identity Commons system is distributed, not centralized. This is not apparent yet because there's only one i-broker, but the code will be released as open source sometime early next year, and anyone will be able to be their own i-broker.
Also keep in mind that other than some minimum amount of information about you (probably password and email address), i-brokers will only store pointers to your personal information. In other words, you'll be able to store your personal data with whomever you
Re:How Come? (Score:2)
Not Passport (words from 2idi) (Score:4, Informative)
As I [xdi.org] like to say, the only thing good about Passport is at least you know their database won't get bought by Microsoft (because they already own it!).
In functionality - such as automatic data sharing, form filling and single sign-on - we share much with Microsoft Passport. (In fact, Passport grew out of Firefly, which is descended from my 1981 thesis on a personalized newspaper - NewsPeek - at what became soon after the M.I.T. Media Lab. I named the systems "NewsPeek" for two reasons: it provided a "peek at the news," and it was a warning that if centralized control over personal profiles existed, the future depicted in George Orwell's 1984 - where the official language was "NewSpeak" - could come true.)
But all that aside, where we differ is where it gets interesting. For one, we are decentralized [fen.net]. There is no single i-broker or data store that you must use. While it is true that there is only one sanctioned global registry for '=' (personal) and '@' (organizational) names, many other forms of community and peer-to-peer i-name registries can exist. It's also important to note that your data is not necessarily stored in any one place. For ease of use reasons you may choose to use a single i-broker to negotiate access to you data, but each item of your profile could conceivably be stored in a different data hosting service. (Note that current service providers that store information about you are acting as a data hosting service already.)
Another point is that, through our architecture and FOSS (free and open source software) availability of our code, we don't lock you in [fen.net]. Rather, you are free to move around between the i-brokers of your choosing - and even to run an i-broker yourself! We (at 2idi [2idi.com]) are committed not only to providing you this choice, but also to providing such a compelling suite of services that i-name holders choose to have their i-names hosted at 2idi.
Re: How Come...well (Score:2)
Central database? (Score:5, Interesting)
Oh, and public lynching of people who use Flash for forms (*cough* UCI Cinemas *cough*).
Re:Central database? (Score:3, Interesting)
To paraphrase an old computer-industry saying:
The nice thing about single-signon schemes is that there are so many to choose from.
Re:Central database? (Score:1)
You'll be able to store your personal data on your own computer. Also, Identity Commons will use the open standard SAML for single sign-on. Several members of the community serve on those committees. There are also folks talking to SXIP and other companies to make sure that it's not YASSO. The reason for this fundraiser is to help build these next pieces of the infrastructure.
Re:Central database? (Score:2, Insightful)
No. The problem with all of the single-signon solutions I've seen is that they make it easy for me to blanket the earth with my personal information. They're solving the problem of how annoying it is to enter the information, but not the problem of how annoying it is to have to enter the information in the first place.
Instead, I want my personal information stored with an escrow agent (such as a bank), and then I want to use the
Re:Central database? (Score:2)
Re:Central database? (Score:1, Interesting)
> congratulations, you have no room to bitch.
And we won't be using your web forms either, learn something about standards, accessability and web application development before misleading clients into putting your garbage on the web. If your web form *needs* javascript, it's broken!
How is this secure? (Score:1)
Keeping the identity private (Score:2)
It's technically possible.. I hope they implement it.
Welcome to Identity Commons (Score:3, Funny)
MS Passport (Score:2)
I personally have tens of usernames and passwords; the important ones are all different (as are the passwords), and the unimportant ones are from a small selection of names. Having only one names means having only one thing that an ID thief needs t
Re:MS Passport (Score:2)
No, it's not. [slashdot.org]
Picks up Steam, eh? (Score:5, Funny)
I wonder how much Valve sold it for.
Re:Picks up Steam, eh? (Score:2)
Late arriving cyber real estate agent (Score:5, Insightful)
The premise is that you pay for a pseudo-permanent identity in cyberspace. Ok, however, the TOS, like most other TOS disclaim any responsibility to consistently deliver the services you're supposedly paying for:
# Although our intention is that this service is always available, 2idi and its licensees and affiliates reserve the right to interrupt or terminate service for some unforeseen circumstance.
# Please note that amendments to this agreement, and to 2idi policies that are incorporated by reference in i-broker agreements, may be made at any time at the sole discretion of 2idi in order to best serve all members of the 2idi community.
The second part is particularly exemplative of the total and utter uselessness of schemes like this. Sure, they want to encourage you to use them as a central repository of personal information, and they allude to respecting your privacy, but they reserve the right, at any time, without your approval, to change the terms of their service, which may arbitrarily involve giving out personal info or whatever they want with whatever they have of yours.
Whenever I evaluate the value of an idea such as this, I consider to what degree the value of the project is based on a useful service, verses the degree to which the success of the project is dependent upon a) obtaining market share and b) marketing. This project fails the test. It doesn't offer anything innovative, and therefore will be marketing driven, and if it doesn't have market share, it will ultimately fail and be useless.
This is one of those markets where it's just too dangerous to fiddle with. For all the resources they invest into this effort, Google, eBay, MSN or Yahoo can pull a similar scheme out of their hat and put them out of business instantly. Spamcop already has a highly effective e-mail/spam forwarding service. The central identity thing has been tried with the
OTOH, what I do like about the basic centralized repository scheme, is that it would be better served as a way to manage and authorize legitimate SMTP servers.
I think we've got a different kind of agent here (Score:3, Insightful) [xns.org] [xns.org] [xdi.org]
The premise is that you pay for a pseudo-permanent identity in cyberspace.
What else have you got? If you don't have your own domain somewhere, that can often times be taken down by your ISP "just because", what else do you have? Your email address. That's pseudo-permanant, right. Is it 50 years permanant? Maybe.
So you tell everyone your email address for a pseudo-permanant identity -
Re:Late arriving cyber real estate agent (Score:2)
The text in the 2idi Terms of Service is, IMO, not the best (disclaimer: I wrote it). I would like to see better text there. Identity Commons is a member governed chaordic org
Re:Late arriving cyber real estate agent (Score:2)
There will be free local i-names available soon (via communities or your own i-broker, once we have the source packaged for release).
Until then, I gotta eat. (And I could make double what I'm making now - and have benefits for my wife and kid - if I quit and worked for some regular company. But I believe in this w
.Net Passport? (Score:1)
Only problem is... I have only ever seen it embraced by Microsoft.
Correct me, if I am confused.
Totalitarianism (Score:1, Insightful)
In the UK at the moment, we are being shaped and molded by a totalitarian government that is effectively reading from the Manual of Marxism. Not only are they stealing our freedoms by the week, but they are fraudulenty manipula
LJ (Score:3, Funny)
huh? LiveJournal? Some angsty teen fearing her AOL screenname got haxored and is now Identity Commonized?!?
Re:LJ (Score:1)
And I don't even have a LiveJournal.
i-Names? (Score:3, Funny)
yet another flat namespace that won't scale (Score:5, Insightful)
Not quite... There's wiggle room. (Score:2)
Thinking about how these things would actually be used, however, it's not so difficult to arrange a way to make it work. People who interact with me are not likely to be interested in the other people with "my" name
Re:Making human names unique (Score:1)
What is generally used to make human names unique is the date of birth. It would be pretty rare to have the same exact name plus the same exact date of birth. Of course, once you have that information, you can do all kinds of nasty things like look that person up in public databases (voter registration, DMV, etc.). So in the end it isn't good to have your i-name reveal anything about you that can be used to find information you don't want to reveal (i.e. address), and definitely not to have it provide infor
Re:Not quite... There's wiggle room. (Score:2)
if they're not globally unique, they're ambiguous.
People who interact with me are not likely to be interested in the other people with "my" name.
It's happened to me, more than once. There used to be someone with the same name as me working for Microsoft. Due to blind trust in directories and address books, I used to get some mail intended for him, and he got some mail intend
Re:yet another flat namespace that won't scale (Score:1)
It's not a flat namespace. There are community i-names as well (under the @ namespace), and you'll be able to subdelegate namespaces under namespaces, such as @blueoxen*eekim.
Not necessary, next please (Score:2)
I'm sure they'll make a few thousand bucks on it, especially after the slashdotting. A few months later, the site silently disappears.
Come on, the "single sign on" idea is flawed anyway. I'm never gonna trust all my data to a single entity, nobody does that - just look at asset management. Diversify your risks.
I don't care about dozens of passw
Re:Not necessary, next please (Score:2)
Re:Not necessary, next please (Score:3, Informative)
People often confuse "single sign-on" with "centrally stored data". The Liberty Alliance solution is different because it is a federated approach based on identity.
In this solution, you identify yourself with a single method. Take for example, 3 different entities you may interact with: your bank, a government agency, and a st
Congratulations (Score:1, Insightful)
The i-name =apple is available.
Looks like a real popular system. Isn't this just RealNames all over again?
Gmail accounts more important than i-names (Score:1)
Google already has the world domination. (Microsoft tried with Passport, didn't work out.)
iNames picks up a steaming pile of poop, maybe (Score:1, Troll)
No way (Score:1)
Seriously, I think companies are going to lose this battle. The internet started life as an anonymous network, and there are many people (myself included) who want to keep things that way. Though it would be co
Not so fast (Score:2, Insightful)
i-Anything (Score:1, Interesting)
PS The e-Thing shit is starting to get annoying as well. Get some creativity and get a real name.
PayPal is probably a better solution (Score:2)
eh, no thanks (Score:4, Insightful)
No way I am willing to be forced into such a thing and even cashing out money for such a wrong purpose.
MS's passport wasn't that good either, but at least I (we) didn't have to pay for it.
Coverage in FUCKING LIVEJOURNAL? (Score:1)
LocalNames (Score:3)
It points names to URL's, but you can use that for identifying purposes. Especially if you mix & match with FOAF. [rdfweb.org]
There are no central registries.
Names are based on the community namespace, rather than some central server.
(That means you don't have to pay me $25, and can address your friends by their first name.)
misconceptions: not centralized nor passport (Score:4, Informative)
Another is that 2idi is just another passport controlling your information. It isn't [fen.net].
It's clear that Identity Commons [identitycommons.net] and 2idi [2idi.com] have to work on their messaging...
No thanks. (Score:2)
I found this particularly telling;
Even assuming for the moment that you could substitute an i-name for an email address, there's no reason to suppose that your i-name wouldn't get just as much spam.
Then there's this;
Re:No thanks. (Score:2)
The good... (Score:2)
fi$hy (Score:2)
Identies are necessary like keys to make sure the entitled party has exclusive access to things that he/she "owns" in whatever sense.
WTF do I own that these 2idi.com people are going to guard for me? They have set up a toll booth in the middle of frigging e-nowhere.net and hope people will still p
Unique-ness in I-Names (Score:2)
How does this avoid duplicates?
I could see where as with DNS you have POC information for the admin type person for this type of configuration you would need more unique information about the indivudal like birthday (time included if possible), birth location, and maybe even some bioinformatic type of information (finger prints, retna scans, etc).
Maybe they should use RFID tags for this type of things kept with each individual. T
Call me Ishmael (Score:2)
Call me Ishmael-7143.
YANANRS? (Score:3, Informative)
I tried to RTFA, but my brain blew a buzzword fuse. How does this differ from the various [igetnet.com] other [com.com] non-authorative [new.net] namespace [commonname.com] resolution [netword.com] schemes [actualnames.com] out there selling cute "internet names" that a majority of machines can't resolve? -more links (Score:2) [idcommons.net]
Re:Another apple product (Score:3, Funny)
Apple? Asimov beat them to it by quite a while - I, Robot.
Re:Another apple product (Score:2) | https://slashdot.org/story/04/12/01/1442236/i-names-pick-up-steam | CC-MAIN-2017-17 | refinedweb | 4,031 | 65.32 |
This doc discusses the various high level components of SJQv4 along with some typical use cases.
The server plugin is installed via the Sage plugin manager and provides the central engine that controls who does what as far as task assignment goes. The server maintains all state information about the SJQ installation, maintains the active task queue, maintains state about all registered task clients, and ultimately decides which task clients are assigned which tasks. The server contains four subsystems, each discussed below.
The timer thread in the server is created when the plugin is started by the core and stopped when the plugin is disabled/uninstalled. The timer then registers all of the various periodic tasks that the server is responsible for running.
The AgenetManager task attempts to connect to each registered task client and issues the PING command on each one. When a response is received, the manager puts the client in ONLINE state and updates the client's details with the response received from the task client. If a task client does not respond or a connection cannot be established then the client is put in OFFLINE state and no other details are updated. Clients in OFFLINE state cannot be assigned tasks. During development, this task is scheduled to run every two minutes and is not configurable. In production, this option will be configurable and a default of 30 or 60 minutes would be likely.
The TaskQueue is triggered via a TimerTask. When triggered, the TaskQueue gets a list of all tasks in WAITING or RETURNED state and attempts to assign them to an ONLINE task client for execution. The TaskQueue is responsible for checking that a potential task client for a given task is:
When a potential task client passes all of these checks it will then send the task to the client.
The cron scheduler is created when the plugin is started and halted when the plugin is stopped. The cron scheduler is configured to read the SageTV/plugins/sjq/crontab file for its scheduling directions. The crontab file is basically a standard *nix crontab file except instead of executing programs, it's used to add tasks to the SJQv4 queue. The Sjq4Crontab wiki doc discusses more details about the format of the crontab and the behaviour of the cron subsystem in SJQv4.
The event listener listens for Sage events and will add tasks to the queue based on the events it receives. I'm still working out the exact implementation details for this subsystem. The Sjq4EventListeners wiki doc will explain the final details of how this subsystem will work.
The server agent is a socket listener that is started when the plugin starts and stopped when the plugin is stopped. The server agent listens for socket connections from either task clients or a ServerClient. These clients can then perform various commands that do things such as update task info, update task log output, add tasks to the task queue, etc. Any entity wishing to read/write from the SJQ server that is not running in the same JVM as the SJQ server MUST communicate via the server agent. Only the server agent guarantees synchronization across both threads and processes. Task clients, STVIs, web interfaces, etc. all must communicate with the SJQ server via the server agent.
The task client is a separate, standalone application that is configured to receive and perform tasks queued up in the SJQ task queue. A task client is configured to perform one or more tasks and waits for the server to assign it tasks. At the highest level, the task client consists of three subsystems.
When started, the task client will create a socket listener on the configured port. The port number must be registered with the server so that the server knows how to contact each task client. This socket listener waits for commands from the server and responds to them. The two major commands a task client responds to are PING and EXE.
Tasks can optionally perform a "pretest" before starting a task execution. This pretest can be used to determine if it's "safe" to perform a given task at assignment time. "Safe" is subjective and can mean anything. A typical safety check might to ensure that there are no clients connected to the SageTV server before starting a certain task.
A pretest can also decide that the assigned task doesn't actually need to be performed and can move the task to SKIPPED state. A typical use case of this feature would be if a task client was assigned a comskip task then the pretest might check for the edl file for the recording and if it's found then it'll put the task in SKIPPED state and not run the comskip.exe on the recording.
All pretests must be a script capable of running in the SJQ scripting environment. The official scripting language of SJQ is Groovy, but users can add support for any other scripting languages supported by Java's JSR-223 scripting API. During development I experimented with Groovy (Java-like), Sleep (Perl-like), Jython (Python), and JavaScript. By far, Groovy was my favourite and is the one I've chosen to support. However, users who prefer other languages are encouraged to use what they know. Support for other languages exist beyond the ones I tested and the Sjq4ScriptingSupport wiki doc goes into much greater detail about the scripting environment in SJQv4.
Finally, a task to be executed is run in the execution environment. Basically, this is just a separate thread spawned that runs the configured exe or SJQ script. The results of this execution determine the final state of the task as reported back to the SJQ server.
This section describes how to get a task to execute on a task client. Each step is described in terms of how the code works, not necessarily how a typical user might accomplish the actions. The idea here is to understand how the code interacts and once you have that, you should be able to envision how to create the UI elements for a user to perform the same set of actions.
I assume a task client is already installed, configured and started. Let's assume the task client is running on host 192.168.0.100 and was configured to run on port 23344.
Registering a task client is relatively straightforward. Create a new Client instance, grab a DataStore connection and save the client to the datastore. You probably want to check that a client isn't already registered at the same host/port combination so as not to overwrite an already existing registration. Mind you, not checking isn't catastrophic as the overwritten data would be restored the next time the server pings the task client.
import com.google.code.sagetvaddons.sjq.shared.Client;
import com.google.code.sagetvaddons.sjq.server.DataStore;
// These values would come from some UI component
String host = "192.168.0.100";
int port = 23334;
DataStore ds = DataStore.get();
Client clnt = ds.getClient(host, port);
if(clnt != null)
System.err.println("ERROR: This client is already registered!");
else
ds.saveClient(new Client(host, port));
The above code is obviously missing error checking, etc.
Now you have a task client registered with the server.
Adding a task to the queue from the web or an STVi means going through a ServerClient connection. In fact, you can always use a ServerClient connection to add tasks to the queue and doing so means you're always going to be properly synchronized. Eventually, the server code will be changed to use ServerClient as well.
import com.google.code.sagetvaddons.sjq.taskqueue.ServerClient;
import com.google.code.sagetvaddons.metadata.Factory;
// You received this input from the user somehow; this is the task type they want
// to add to the task queue
String taskId = "MYTASK";
// This is a reference to some Sage object they want to associate with the task;
// if they queued this task from a recording details page, for example, then this would
// be a reference to a MediaFile object. Assume it's already been set somehow.
Object sageObj;
ServerClient clnt = new ServerClient();
long id = clnt.addTask(taskId, Factory.getMap(sageObj));
clnt.close();
System.out.println("Task " + id + " was added to the queue!");
Of interest in this code:
Your job is done! :) You've now registered a task client and inserted a task into the queue. Just make sure the task client you've registered is configured to accept tasks of type MYTASK and as long as it is, the server should assign the task to the task client.
The other interesting things all come from ServerClient. You use ServerClient to read the active queue, get a list of registered task clients, etc. Actually, that's all it does for now, but over the coming weeks additional features like deleting tasks from the queue, cancelling running tasks, etc. will all be added to ServerClient. Hopefully, it becomes clear that everything you need to do is done through DataStore and ServerClient. | http://code.google.com/p/sagetv-addons/wiki/Sjq4DesignAndImplementation | crawl-003 | refinedweb | 1,509 | 62.98 |
We are about to switch to a new forum software. Until then we have removed the registration on this forum.
Hello, I am relatively new to Processing and even newer in Arduino. I have two buttons on my Arduino board and want to be able to move left & right a rectangle in Processing.
My mini Processing sketch looks like this
import processing.serial.*; Serial myPort; // Create object from Serial class int val; // Data received from the serial port int x=50; void setup() { size(200, 200); String portName = Serial.list()[5]; myPort = new Serial(this, portName, 9600); } void draw() { if ( myPort.available() > 0) { // If data is available, val = myPort.read(); // read it and store it in val } background(255); // Set background to white if (val == 1) { x = x-1; } if (val ==2) { x = x+1; } rect(x, 50, 100, 100); }
and my Arduino sketch like this
int switchPin1 = 2; // Switch connected to pin 4 int switchPin2 = 3; // Switch connected to pin 4 void setup() { pinMode(switchPin1, INPUT); // Set pin 0 as an input pinMode(switchPin2, INPUT); Serial.begin(9600); // Start serial communication at 9600 bps } void loop() { if (digitalRead(switchPin1) == HIGH) { // If switch is ON, Serial.write(1); // send 1 to Processing } else { // If the switch is not ON, Serial.write(0); // send 0 to Processing } if (digitalRead(switchPin2) == HIGH) { // If switch is ON, Serial.write(2); // send 1 to Processing } else { // If the switch is not ON, Serial.write(3); // send 0 to Processing } delay(100); // Wait 100 milliseconds }
It is working but I don't think that is the right way to do it since when I move to the right, it moves smoothly but when I try the x = x-1, it goes very slowly, can someone tell me what am I doing wrong?
Answers
this
better
this
better
I am afraid that only makes things worse! :(
sorry...
I don't know....
why don't include all in the if clause?
with the delay (100); You send only one "write (2)" and various "write (3) (else the first button) or eliminate the "else", or enter two delay, to make the first and second button with equal time
Thanks for your reply, I ended up using the Serial Call Response example from the Arduino communication examples! | https://forum.processing.org/two/discussion/11076/processing-arduino-buttons | CC-MAIN-2020-45 | refinedweb | 378 | 68.81 |
Introduction to parallel MCMC for Bayesian inference, using C, MPI, the GSL and SPRNG
Introduction
This post is aimed at people who already know how to code up Markov Chain Monte Carlo (MCMC) algorithms in C, but are interested in how to parallelise their code to run on multi-core machines and HPC clusters. I discussed different languages for coding MCMC algorithms in a previous post. The advantage of C is that it is fast, standard and has excellent scientific library support. Ultimately, people pursuing this route will be interested in running their code on large clusters of fast servers, but for the purposes of development and testing, this really isn’t necessary. A single dual-core laptop, or similar, is absolutely fine. I develop and test on a dual-core laptop running Ubuntu linux, so that is what I will assume for the rest of this post.
There are several possible environments for parallel computing, but I will focus on the Message-Passing Interface (MPI). This is a well-established standard for parallel computing, there are many implementations, and it is by far the most commonly used high performance computing (HPC) framework today. Even if you are ultimately interested in writing code for novel architectures such as GPUs, learning the basics of parallel computation using MPI will be time well spent.
MPI
The whole point of MPI is that it is a standard, so code written for one implementation should run fine with any other. There are many implementations. On Linux platforms, the most popular are OpenMPI, LAM, and MPICH. There are various pros and cons associated with each implementation, and if installing on a powerful HPC cluster, serious consideration should be given to which will be the most beneficial. For basic development and testing, however, it really doesn’t matter which is used. I use OpenMPI on my Ubuntu laptop, which can be installed with a simple:
sudo apt-get install openmpi-bin libopenmpi-dev
That’s it! You’re ready to go… You can test your installation with a simple “Hello world” program such as:
#include <stdio.h> #include <mpi; }
You should be able to compile this with
mpicc -o helloworld helloworld.c
and run (on 2 processors) with
mpirun -np 2 helloworld
GSL
If you are writing non-trivial MCMC codes, you are almost certainly going to need to use a sophisticated math library and associated random number generation (RNG) routines. I typically use the GSL. On Ubuntu, the GSL can be installed with:
sudo apt-get install gsl-bin libgsl0-dev
A simple script to generate some non-uniform random numbers is given below.
#include <gsl/gsl_rng.h> #include <gsl/gsl_randist.h> int main(void) { int i; double z; gsl_rng *r; r = gsl_rng_alloc(gsl_rng_mt19937); gsl_rng_set(r,0); for (i=0;i<10;i++) { z = gsl_ran_gaussian(r,1.0); printf("z(%d) = %f\n",i,z); } exit(EXIT_SUCCESS); }
This can be compiled with a command like:
gcc gsl_ran_demo.c -o gsl_ran_demo -lgsl -lgslcblas
and run with
./gsl_ran_demo
SPRNG
When writing parallel Monte Carlo codes, it is important to be able to use independent streams of random numbers on each processor. Although it is tempting to “fudge” things by using a random number generator with a different seed on each processor, this does not guarantee independence of the streams, and an unfortunate choice of seeds could potentially lead to bad behaviour of your algorithm. The solution to this problem is to use a parallel random number generator (PRNG), designed specifically to give independent streams on different processors. Unfortunately the GSL does not have native support for such parallel random number generators, so an external library should be used. SPRNG 2.0 is a popular choice. SPRNG is designed so that it can be used with MPI, but also that it does not have to be. This is an issue, as the standard binary packages distributed with Ubuntu (libsprng2, libsprng2-dev) are compiled without MPI support. If you are going to be using SPRNG with MPI, things are simpler with MPI support, so it makes sense to download sprng2.0b.tar.gz from the SPRNG web site, and build it from source, carefully following the instructions for including MPI support. If you are not familiar with building libraries from source, you may need help from someone who is.
Once you have compiled SPRNG with MPI support, you can test it with the following code:
#include <stdio.h> #include <stdlib.h> #include <mpi.h> #define SIMPLE_SPRNG #define USE_MPI #include "sprng.h" int main(int argc,char *argv[]) { double rn; int i,k; MPI_Init(&argc,&argv); MPI_Comm_rank(MPI_COMM_WORLD,&k); init_sprng(DEFAULT_RNG_TYPE,0,SPRNG_DEFAULT); for (i=0;i<10;i++) { rn = sprng(); printf("Process %d, random number %d: %f\n", k, i+1, rn); } MPI_Finalize(); exit(EXIT_SUCCESS); }
which can be compiled with a command like:
mpicc -I/usr/local/src/sprng2.0/include -L/usr/local/src/sprng2.0/lib -o sprng_demo sprng_demo.c -lsprng -lgmp
You will need to edit paths here to match your installation. If if builds, it can be run on 2 processors with a command like:
mpirun -np 2 sprng_demo
If it doesn’t build, there are many possible reasons. Check the error messages carefully. However, if the compilation fails at the linking stage with obscure messages about not being able to find certain SPRNG MPI functions, one possibility is that the SPRNG library has not been compiled with MPI support.
The problem with SPRNG is that it only provides a uniform random number generator. Of course we would really like to be able to use the SPRNG generator in conjunction with all of the sophisticated GSL routines for non-uniform random number generation. Many years ago I wrote a small piece of code to accomplish this, gsl-sprng.h. Download this and put it in your include path for the following example:
#include <mpi.h> #include <gsl/gsl_rng.h> #include "gsl-sprng.h" #include <gsl/gsl_randist.h> int main(int argc,char *argv[]) { int i,k,po; gsl_rng *r; MPI_Init(&argc,&argv); MPI_Comm_rank(MPI_COMM_WORLD,&k); r=gsl_rng_alloc(gsl_rng_sprng20); for (i=0;i<10;i++) { po = gsl_ran_poisson(r,2.0); printf("Process %d, random number %d: %d\n", k, i+1, po); } MPI_Finalize(); exit(EXIT_SUCCESS); }
A new GSL RNG, gsl_rng_sprng20 is created, by including gsl-sprng.h immediately after gsl_rng.h. If you want to set a seed, do so in the usual GSL way, but make sure to set it to be the same on each processor. I have had several emails recently from people who claim that gsl-sprng.h “doesn’t work”. All I can say is that it still works for me! I suspect the problem is that people are attempting to use it with a version of SPRNG without MPI support. That won’t work… Check that the previous SPRNG example works, first.
I can compile and run the above code with
mpicc -I/usr/local/src/sprng2.0/include -L/usr/local/src/sprng2.0/lib -o gsl-sprng_demo gsl-sprng_demo.c -lsprng -lgmp -lgsl -lgslcblas mpirun -np 2 gsl-sprng_demo
Parallel Monte Carlo
Now we have parallel random number streams, we can think about how to do parallel Monte Carlo simulations. Here is a simple example:
#include <math.h> #include <mpi.h> #include <gsl/gsl_rng.h> #include "gsl-sprng.h" int main(int argc,char *argv[]) { int i,k,N; double u,ksum,Nsum; gsl_rng *r; MPI_Init(&argc,&argv); MPI_Comm_size(MPI_COMM_WORLD,&N); MPI_Comm_rank(MPI_COMM_WORLD,&k); r=gsl_rng_alloc(gsl_rng_sprng20); for (i=0;i<10000;i++) { u = gsl_rng_uniform(r); ksum += exp(-u*u); } MPI_Reduce(&ksum,&Nsum,1,MPI_DOUBLE,MPI_SUM,0,MPI_COMM_WORLD); if (k == 0) { printf("Monte carlo estimate is %f\n", (Nsum/10000)/N ); } MPI_Finalize(); exit(EXIT_SUCCESS); }
which calculates a Monte Carlo estimate of the integral
using 10k variates on each available processor. The MPI command MPI_Reduce is used to summarise the values obtained independently in each process. I compile and run with
mpicc -I/usr/local/src/sprng2.0/include -L/usr/local/src/sprng2.0/lib -o monte-carlo monte-carlo.c -lsprng -lgmp -lgsl -lgslcblas mpirun -np 2 monte-carlo
Parallel chains MCMC
Once parallel Monte Carlo has been mastered, it is time to move on to parallel MCMC. First it makes sense to understand how to run parallel MCMC chains in an MPI environment. I will illustrate this with a simple Metropolis-Hastings algorithm to sample a standard normal using uniform proposals, as discussed in a previous post. Here an independent chain is run on each processor, and the results are written into separate files.
#include <gsl/gsl_rng.h> #include "gsl-sprng.h" #include <gsl/gsl_randist.h> #include <mpi.h> int main(int argc,char *argv[]) { int k,i,iters; double x,can,a,alpha; gsl_rng *r; FILE *s; char filename[15]; MPI_Init(&argc,&argv); MPI_Comm_rank(MPI_COMM_WORLD,&k); if ((argc != 3)) { if (k == 0) fprintf(stderr,"Usage: %s <iters> <alpha>\n",argv[0]); MPI_Finalize(); return(EXIT_FAILURE); } iters=atoi(argv[1]); alpha=atof(argv[2]); r=gsl_rng_alloc(gsl_rng_sprng20); sprintf(filename,"chain-%03d.tab",k); s=fopen(filename,"w"); if (s==NULL) { perror("Failed open"); MPI_Finalize(); return(EXIT_FAILURE); } x = gsl_ran_flat(r,-20,20); fprintf(s,"Iter X\n"); for (i=0;i<iters;i++) { can = x + gsl_ran_flat(r,-alpha,alpha); a = gsl_ran_ugaussian_pdf(can) / gsl_ran_ugaussian_pdf(x); if (gsl_rng_uniform(r) < a) x = can; fprintf(s,"%d %f\n",i,x); } fclose(s); MPI_Finalize(); return(EXIT_SUCCESS); }
I can compile and run this with the following commands
mpicc -I/usr/local/src/sprng2.0/include -L/usr/local/src/sprng2.0/lib -o mcmc mcmc.c -lsprng -lgmp -lgsl -lgslcblas mpirun -np 2 mcmc 100000 1
Parallelising a single MCMC chain
The parallel chains approach turns out to be surprisingly effective in practice. Obviously the disadvantage of that approach is that “burn in” has to be repeated on every processor, which limits how much efficiency gain can be acheived by running across many processors. Consequently it is often desirable to try and parallelise a single MCMC chain. As MCMC algorithms are inherently sequential, parallelisation is not completely trivial, and most (but not all) approaches to parallelising a single MCMC chain focus on the parallelisation of each iteration. In order for this to be worthwhile, it is necessary that the problem being considered is non-trivial, having a large state space. The strategy is then to divide the state space into “chunks” which can be updated in parallel. I don’t have time to go through a real example in detail in this blog post, but fortunately I wrote a book chapter on this topic almost 10 years ago which is still valid and relevant today. The citation details are:
Wilkinson, D. J. (2005) Parallel Bayesian Computation, Chapter 16 in E. J. Kontoghiorghes (ed.) Handbook of Parallel Computing and Statistics, Marcel Dekker/CRC Press, 481-512.
The book was eventually published in 2005 after a long delay. The publisher which originally commisioned the handbook (Marcel Dekker) was taken over by CRC Press before publication, and the project lay dormant for a couple of years until the new publisher picked it up again and decided to proceed with publication. I have a draft of my original submission in PDF which I recommend reading for further information. The code examples used are also available for download, including several of the examples used in this post, as well as an extended case study on parallelisation of a single chain for Bayesian inference in a stochastic volatility model. Although the chapter is nearly 10 years old, the issues discussed are all still remarkably up-to-date, and the code examples all still work. I think that is a testament to the stability of the technology adopted (C, MPI, GSL). Some of the other handbook chapters have not stood the test of time so well.
For basic information on getting started with MPI and key MPI commands for implementing parallel MCMC algorithms, the above mentioned book chapter is a reasonable place to start. Read it all through carefully, run the examples, and carefully study the code for the parallel stochastic volatility example. Once that is understood, you should find it possible to start writing your own parallel MCMC algorithms. For further information about more sophisticated MPI usage and additional commands, I find the annotated specification: MPI – The complete reference to be as good a source as any.
18 thoughts on “Getting started with parallel MCMC”
Please please please stop using LAM/MPI.
We’ve wholly replaced it with Open MPI these days. :-)
Hi,
That’s a really informative blog. I am trying to parallelise MCMC in a bioinformatics software using OpenMPI. After deep analysis, I realised that within each iteration of the MCMC loop, the steps are sequential and hence I cannot parallelise a single MCMC chain. hence, I am trying to implement the multiple chain approach. However, I am not able to understand that how should the results be combined from the smaller multiple chains to obtain the final results?
Any help would be greatly appreciated. Thanks!
Essentially, after discarding burn-in from the start of each chain, all of your samples should be from the desired posterior, and hence can be pooled for analysis. However, it can be helpful to keep the chains separate for diagnostic purposes. The R “coda” package will read in parallel chains and conduct diagnostic analysis and inference for you.
Thanks for the reply. My query is how to ‘pool for analysis’ to obtain a single chain like behaviour from the multiple chains?
for eg, if i obtain the following chains:
chain1: x1,x2,x3…
chain2: y1,y2,y3…
chain3: z1,z2,z3…
How should i combine them to obtain a single chain?
In some sense it doesn’t matter. So, for example, you could concatenate the chains, as:
x1,x2,x3,…y1,y2,y3,…,z1,z2,z3,…
but I would strongly recommend that you take a look at the “coda” package mentioned above for methods to analyse the chains in parallel
thanks
Can you provide an example of how a bad parallel RNG affects the results of MC. Also can you add openMP into the mix as well since it is more likely that single computer owners will be using openMP rather than MPI which is meant for large clusters.
Thank you so munch for sharing, that’s very helpful.
Now, I’m wondering if it’s possible to proceed the same way using MKL in order to generate arrays of random numbers in parallel. I use both GSL and MKL on one node and found to get a bunch of random number at once very convenient. So, having the possibility to do this in parallel would be very great, like getting one random array per node.
I’ll definitely implement your code above first.
Thanks again. Eric. | https://darrenjw.wordpress.com/2010/12/14/getting-started-with-parallel-mcmc/ | CC-MAIN-2015-35 | refinedweb | 2,466 | 53.92 |
With Ardouno IDE 2.0.0 beta7: Compile and upload works.
According to the description, the multi-color LED should be switched on and off. As described, I entered '1' and '0', text is displayed, but the LED does nothing.
With Ardouno IDE 2.0.0 beta7: Compile and upload works.
Please post the code so that we don't have to guess what you are referring to
Are you a robot? I cannot assess this answer otherwise!
Why should I copy here an example that can be reached in the IDE with 2 mouse clicks?
Have it your own way and do not make it as easy as possible to provide help
All of those examples build elf and not uf2 for me - so it's definitely not running for me.
WARNING: library Scheduler claims to run on mbed architecture(s) and may be incompatible with your current board which runs on mbed_nano architecture(s). Sketch uses 79452 bytes (0%) of program storage space. Maximum is 16777216 bytes. Global variables use 53348 bytes (19%) of dynamic memory, leaving 216988 bytes for local variables. Maximum is 270336 bytes. /home/user/.arduino15/packages/arduino/tools/rp2040tools/1.0.2/rp2040load -v -D /tmp/arduino_build_210032/MultipleBlinks.ino.elf
Not sure if you're having the same problem but they do not even load directly from the Arduino IDE for me.
Here's what I had to do to get MultipleBlinks to load.
- Export the binary through the UI
- Find elf2utf2 (mine was in ~/.arduino15/packages/arduino/tools/rp2040tools/1.0.2/elf2utf2)
- Run elf2utf2 against the exported binary
- Put the Connect in bootloader mode (hit the button twice)
- Copy the utf2 binary to the storage device
When it comes back online it still doesn't work. You can use the serial port to type '0' or '1' like the example says and you'll see "Led turned off!" but nothing happens with the RGB LED.
Edit: Nothing happens because those pins aren't defined in the pins.h for this board
Hello all.
Here's the sketch:
#include <Scheduler.h> int led1 = LEDR; int led2 = LEDG; int led3 = LEDB; void setup() { Serial.begin(9600); // Setup the 3 pins as OUTPUT pinMode(led1, OUTPUT); pinMode(led2, OUTPUT); pinMode(led3, OUTPUT); // Add "loop2" and "loop3" to scheduling. // "loop" is always started by default. Scheduler.startLoop(loop2); Scheduler.startLoop(loop3); } // Task no.1: blink LED with 1 second delay. void loop() { digitalWrite(led1, HIGH); // IMPORTANT: // When multiple tasks are running 'delay' passes control to // other tasks while waiting and guarantees they get executed. delay(1000); digitalWrite(led1, LOW); delay(1000); } // Task no.2: blink LED with 0.1 second delay. void loop2() { digitalWrite(led2, HIGH); delay(100); digitalWrite(led2, LOW); delay(100); } // Task no.3: accept commands from Serial port // '0' turns off LED // '1' turns on LED void loop3() { if (Serial.available()) { char c = Serial.read(); if (c == '0') { digitalWrite(led3, LOW); Serial.println("Led turned off!"); } if (c == '1') { digitalWrite(led3, HIGH); Serial.println("Led turned on!"); } } // IMPORTANT: // We must call 'yield' at a regular basis to pass // control to other tasks. yield(); }
Here's the fix:
In order to make this sketch work for the Nano RP2040 Connect, it's necessary to change these lines:
int led1 = LEDR; int led2 = LEDG; int led3 = LEDB;
to this:
#include <WiFiNINA.h> NinaPin led1 = LEDR; NinaPin led2 = LEDG; NinaPin led3 = LEDB;
Why is the WiFiNINA library needed?
The Nano RP2040 Connect uses the u-blox NINA-W102 module for Wi-Fi connectivity. But this module is also just a standard ESP32 microcontroller. No reason to let those precious GPIO pins go to waste. So the RGB LED is connected to the NINA module, rather than taking up the RP2040 pins. So in order to blink these LEDs it's necessary for the RP2040 to communicate with the NINA module. That communication is handled by the WiFiNINA library.
This is described in the technical reference.
Why is the
NinaPin type needed?
You can see that the NINA's pins are controlled by the familiar Arduino language
pinMode() and
digitalWrite()functions. But under the hood, this works quite differently when controlling these pins vs the RP2040's pins. The WiFiNINA library provides function overloads that use the
NinaPin type for the pin number parameter instead of the usual
PinName type:
There appears to be work in progress to improve on this situation with the Scheduler library:
To Pert: Thank you, this 4 lines where very helpful. I will remember your instructions at further experiments.
You're welcome. I'm glad if I was able to be of assistance.
Back with the inevitable (??) changes with Arduino - why?
This no longer works with nano_embed/2.2.0!
NanoPin has been changed to a class.
Why are working parts changed over and over again?
The change to a class was made in the pull request I linked to in my original reply. The description in that pull request provides an explanation for why the change was made:
Some sketches use a pattern like
int potpin = A5
Since NinaPin was an enum, the implicit cast was taking place, and any subsequent call to analogRead() would not use the Nina functions. | https://forum.arduino.cc/t/example-multipleblinks-does-not-work-solved-2nd/865075/7 | CC-MAIN-2021-31 | refinedweb | 869 | 67.45 |
.
Let’s explore this with the help of below code block
using System; using System.Collections.Generic; using System.Linq; using System.Text; namespace CreateObjectIDDemoApps { class Program { static void Main(string[] args) { List<Student> students = new List<Student> { new Student { Roll = 1, Name = "Abhijit", Address = "Hyderabad" }, new Student { Roll = 2, Name = "Kunal", Address = "Pune" }, new Student { Roll = 3, Name = "Abhishek", Address = "Kolkata" }, new Student { Roll = 4, Name = "Rahul", Address = "Delhi" } }; foreach (Student stud in students) { Console.Write(stud.ToString()); } } class Student { public int Roll { get; set; } public string Name { get; set; } public string Address { get; set; } public override string ToString() { return "Roll : " + this.Roll.ToString() + "\tName : " + this.Name + "\tAddress : " + this.Address + "\n"; } } } }
As per the above code we have a list of Student object. I will show you how we can create new object ID for any specific object and can track them even though went out of scope.
Creating Object ID
To make an Object Id, You have to view the object from Watch Window, then Right Click > Context Menu, select “Make Object ID”.
The watch window will display a number with the pound (#) sign .
The Object ID number will increment based on the object ID Creation. Which means for the next object ID the identification number will be like 2#,3# etc.
Using Object ID
You have already created an Object ID ( 1#) for a particular student object from list of Student objects. let’s have a look how to use that object Id. You can easily type the object id in watch window to get the details value of that object.
So as per the above image you can see 1# object ID showing the details of the student object with Roll= 1, for which we have created that Object ID.
If you look into the details, you can see, though current break point showing the student details with Roll=3, still 1# Object ID pointing to Student Object with Roll 1, because of 1# object id now uniquely identifying one of the student object.
Creating and Using Object ID for Multiple Objects
You can create and use the multiple Object ID using same process that I have discussed. If you want to keep track of more than one object you can use it.
When Object goes Out of Scope ?
Till now I have discussed how to create an Object Id and How to use them. Now let’s discuss about the actual use if Object ID. As I have already said,”Object Id is used to track any object even if the object is Out of Scope”. In my above example both the object ID and the actual object was in the scope of current context. Let’s have a look when the object goes out of scope and what is the behavior of Object ID on that time.
To explore this, Just put a break point out side of foreach statement, where “stud” object is not in the scope. Run the application and Create an object Id for the first object of student lists. Wait till when debugger hits the breakpoint next to foreach statement.
Above image is the quick summary of the track of object when object goes out of scope. From the image you can see, “Stud” object is not getting evaluated as it is not in the current scope, but Object ID (1#) is still active which show the actual values of the object for which ID was created. You can also click on the “Refresh” icon with the values of “stud” object to get the updated value. But, If you click on that icon, you will get the message “The name ‘stud’ does not exist in the current context” as shown in below.
But you can get the same object values from the Object ID. Though your actual object goes out of scope but it’s not collected by the GC, Object ID still keep the track of that object as the object still present in memory. You will get the message “Can’t evaluated object” once the actual object collected by the GC.
Working with “Out Of Scope” Object ?
You can access any variables or methods from the object Id’s as ((ClassName)ObjectID#).Properties or ((ClassName)ObjectID#).Method(). As per our example we can access Roll for that Object as shown in below
Similarly we can access the same variables from “Immediate Window” as well.
Conditional Break Point with Object ID
You can also set conditional break points with the created object Ids. I have explained about how to use conditional break points over Mastering in Visual Studio 2010 Debugging – Conditional Breakpoint article. We have to use the same way that I have mentioned while discussed about the accessing Object ID.
Above conditions tell the Visual Studio Debugger that, If the Object with Object ID 1# having Roll =1, then only hit the break point.
Note: While using Conditional breakpoint you have to make sure you are creating the Object ID before debugger hit the conditional break points. Otherwise you will get the error message with “Object ID not found” as shown in below
Delete Object ID
You can delete the object using the similar way that you have used for the creating an Object Id. Right Click on the Object Instance for which you have already created the Object Id, you will get “Delete Object ID” Option
If you delete the Object Id with a specific number does not means the next created ID will be the same ID that You have deleted. which means, Let say, you have 3 Object ID’s 1#, 2# and 3#. You have delete the object ID 2#. Now if you create another new Object ID, new ID will be 4# not 2#. Which indicates, one Object ID is used to uniquely Identify a particular object Instance, not for the same object again or for other object. The same ID can only be used once GC collects that object.
Summary : In this blog post I have explained how we can use Object ID to keep track of an Out of Scope Object. By using “Make Object ID” option we are informing Visual Studio Debugger to Keep track of that object no matter it’s within scope or out of scope. When we create Object ID for an particular object, Visual Studio Debugger ( CLR Debugging Services ) use an integer value to uniquely identify the object. This “Object ID” allows you to get the object details even if it is out of scope. If you received the message “Can’t evaluate the Object Values” while working with “Object ID”, it means that Object has been garbage collected. This is another way where you can identify that an Object has been garbage collected.
Hope this will help you !
Thanks !
AJ
20 thoughts on “How to track an object which is Out of Scope while Debugging ?”
Nice stuff Man!!
Keep it up!!!
Thanks Brij !
How to track an object which is Out of Scope while Debugging ? « Abhijit’s World of .NET…
Thank you for submitting this cool story – Trackback from DotNetShoutout…
[…] How to track an object which is Out of Scope while Debugging – Abhijit Jana looks at the use of Object ID Generation in the Visual Studio Debugger showing how it allows you to keep watches on objects regardless of the current scope showing it in use with plenty of screenshots for illustration. […]
AJ,
Great post.
I’ll have to go an try this out myself. It’s one thing to read about it, do it makes it real (at least that how it works for me).
Thanks,
I look forward to more handy tips.
Craig
[…] How to track an object which is Out of Scope while Debugging ? (Abhijit Jana) […]
[…] How to track an object which is Out of Scope while Debugging – Abhijit Jana […]
Very useful post – thanks a bunch :)
Thanks Sean !
How can I follow you on Twitter? Excellent Article, thank you!
Thanks ! My Twitter id is @AbhijitJana.
[…] How to track an object which is Out of Scope while Debugging ? […]
[…] How to track an object which is Out of Scope while Debugging ? […]
[…] How to track an object which is Out of Scope while Debugging ? « Abhijit’s World of .NET. […]
[…] to understand how to use Object ID to track and out of scope object. Here is my complete article How to track an object which is Out of Scope while Debugging ? . Though I described a quick look into use of out of scope object inside conditional breakpoints on […]
Exactly what I was looking for! I have no idea how Bing ranks your blog for How to track an object which is Out of Scope while Debugging ? Abhijit's World of .NET. That’s actually great!
[…] to understand how to use Object ID to track and out of scope object. Here is my complete article How to track an object which is Out of Scope while Debugging ? . Let’s consider we have below code […]
Very interesting. There’s another way to do something similar to this. Suppose your in some random debugger context and want to call a method “isValid” that takes an integer argument (ex: 23), is in the namespace “BAR”, and lives in the “foo” DLL. You can call it by typing this in the watch window: {,,foo}BAR::isValid(23)
Denis, that sounds good. Let me try the same.
[…] ? […] | http://abhijitjana.net/2010/10/20/how-to-track-an-object-which-is-out-of-scope-while-debugging/ | CC-MAIN-2015-11 | refinedweb | 1,565 | 71.44 |
I'm trying to create a program that lets me search certain strings, is this the write setup?
Import urllib.request
import urllib2
import re
htmlcontent = urllib2.urlopen('URL').read()
matches = re.findall('regex of string to find', str1 =);
if len(matches) == 0:
print 'I did not find anything'
else:
print 'The string is in the url'
I don't know Python, I looked the code up for help. Please someone tell me if this is correct, I can't run it right now just wondering. Please and Thanks. :D
2 Responses
Typo, write is suppose to be right...
Wrong Comment.
Share Your Thoughts | https://null-byte.wonderhowto.com/forum/python-correct-0166388/ | CC-MAIN-2018-09 | refinedweb | 104 | 76.42 |
SAX parsers implement the XMLReader interface. They are implemented in a Python module, which must provide a function create_parser(). This function is invoked by xml.sax.make_parser() with no arguments to create a new parser object.
Base class which can be inherited by SAX parsers..
Interface for associating a SAX event with a document location. A locator object will return valid results only during calls to DocumentHandler methods; at any other time, the results are unpredictable. If information is not available, methods may return None..
This is an implementation of the Attributes interface (see section The Attributes Interface). This is a dictionary-like object which represents the element attributes in a startElement() call. In addition to the most useful dictionary operations, it supports a number of other methods as described by the interface. Objects of this class should be instantiated by readers; attrs must be a dictionary-like object containing a mapping from attribute names to attribute values.
Namespace-aware variant of AttributesImpl, which will be passed to startElementNS(). It is derived from AttributesImpl, but understands attribute names as two-tuples of namespaceURI and localname. In addition, it provides a number of methods expecting qualified names as they appear in the original document. This class implements the AttributesNS interface (see section The AttributesNS Interface).
The XMLReader interface supports the following methods:
Process an input source, producing SAX events. The source object can be a system identifier (a string identifying the input source – typically a file name or an URL), a file-like object, or an InputSource object. When parse() returns, the input is completely processed, and the parser object can be discarded or reset. As a limitation, the current implementation only accepts byte streams; processing of character streams is for further study.
Return the current ContentHandler.
Set the current ContentHandler. If no ContentHandler is set, content events will be discarded.
Return the current DTDHandler.
Set the current DTDHandler. If no DTDHandler is set, DTD events will be discarded.
Return the current EntityResolver.
Set the current EntityResolver. If no EntityResolver is set, attempts to resolve an external entity will result in opening the system identifier for the entity, and fail if it is not available.
Return the current ErrorHandler.
Set the current error handler. If no ErrorHandler is set, errors will be raised as exceptions, and warnings will be printed.
Allow an application to set the locale for errors and warnings.
SAX parsers are not required to provide localization for errors and warnings; if they cannot support the requested locale, however, they must raise a SAX exception. Applications may request a locale change in the middle of a parse.
Return the current setting for feature featurename. If the feature is not recognized, SAXNotRecognizedException is raised. The well-known featurenames are listed in the module xml.sax.handler.
Set the featurename to value. If the feature is not recognized, SAXNotRecognizedException is raised. If the feature or its setting is not supported by the parser, SAXNotSupportedException is raised.
Return the current setting for property propertyname. If the property is not recognized, a SAXNotRecognizedException is raised. The well-known propertynames are listed in the module xml.sax.handler.
Set the propertyname to value. If the property is not recognized, SAXNotRecognizedException is raised. If the property or its setting is not supported by the parser, SAXNotSupportedException is raised.
Instances of IncrementalParser offer the following additional methods:
Process a chunk of data.
Assume the end of the document. That will check well-formedness conditions that can be checked only at the end, invoke handlers, and may clean up resources allocated during parsing.
This method is called after close has been called to reset the parser so that it is ready to parse new documents. The results of calling parse or feed after close without calling reset are undefined.
Instances of Locator provide these methods:
Return the column number where the current event ends.
Return the line number where the current event ends.
Return the public identifier for the current event.
Return the system identifier for the current event.
Sets the public identifier of this InputSource.
Returns the public identifier of this InputSource.
Sets the system identifier of this InputSource.
Returns the system identifier of this InputSource.
Sets the character encoding of this InputSource.
The encoding must be a string acceptable for an XML encoding declaration (see section 4.3.3 of the XML recommendation).
The encoding attribute of the InputSource is ignored if the InputSource also contains a character stream.
Get the character encoding of this InputSource..
Get the character stream for this input source.
Attributes objects implement a portion of the mapping protocol, including the methods copy(), get(), __contains__(), items(), keys(), and values(). The following methods are also provided:
Return the number of attributes.
Return the names of the attributes.
Returns the type of the attribute name, which is normally 'CDATA'.
Return the value of attribute name.
This interface is a subtype of the Attributes interface (see section The Attributes Interface). All methods supported by that interface are also available on AttributesNS objects.
The following methods are also available:
Return the value for a qualified name.
Return the (namespace, localname) pair for a qualified name.
Return the qualified name for a (namespace, localname) pair.
Return the qualified names of all attributes. | http://www.wingware.com/psupport/python-manual/3.3/library/xml.sax.reader.html | CC-MAIN-2015-32 | refinedweb | 876 | 51.65 |
Multi-threading is very popular topic among interviewers from long time. Though I personally feel that very few of us get real chance to work on a complex multi-threaded application (I got only one chance in last 7 years), still it helps in having the concepts handy to boost your confidence ONLY. Previously, I discussed a similar question about difference between wait() and sleep() method, this time I am discussing difference between join() and yield() methods. Frankly speaking, I have not used any of both methods in practical so please make a argument if you feel otherwise at any point.
A little background on java thread scheduling
A Java virtual machine is required to implement a preemptive, priority-based scheduler among its various threads. This means that each thread in a Java program is assigned a certain priority, a positive integer that falls within a well-defined range. This priority can be changed by the developer. The Java virtual machine never changes the priority of a thread, even if the thread has been running for a certain period of time.
The priority value is important because the contract between the Java virtual machine and the underlying operating system is that the operating system must generally choose to run the Java thread with the highest priority. That’s what we mean when we say that Java implements a priority-based scheduler. This scheduler is implemented in a preemptive fashion, meaning that when a higher-priority thread comes along, that thread interrupts (preempts) whatever lower-priority thread is running at the time. The contract with the operating system, however, is not absolute, which means that the operating system can sometimes choose to run a lower-priority thread. [I hate this about multi-threading.. nothing is guaranteed :-( ]
Also note that java does not mandate that its threads be time-sliced, but most operating systems do so. There is often some confusion in terminology here: preemption is often confused with time-slicing. In fact, preemption means only that a higher-priority thread runs instead of a lower-priority one, but when threads have the same priority, they do not preempt each other. They are typically subject to time-slicing, but that is not a requirement of Java.
Understanding thread priorities
Understanding the Thread priorities is next important step in learning Multi-threading and specially how yield() works.
-.
Now when we have some basic understanding of thread scheduling and thread priorities, let’s jump into subject.
yield() method. */ public static native void yield();
Let’s list down important points from above definition:
- Yield is a Static method and Native too.
- Yield tells the currently executing thread to give a chance to the threads that have equal priority in the Thread Pool.
- There is no guarantee that Yield will make the currently executing thread to runnable state immediately.
- It can only make a thread from Running State to Runnable State, not in wait or blocked state.
yield() method example usage
In below example program, I have created two threads named producer and consumer for no specific reason. Producer is set to minimum priority and consumer is set to maximum priority. I will run below code with/without commenting the line Thread.yield(). Without yield(), though the output changes sometimes, but usually first all consumer lines are printed and then all producer lines.
With using yield() method, both prints one line at a time and pass the chance to another thread, almost all the time.
package test.core.threads; public class YieldExample { public static void main(String[] args) { Thread producer = new Producer(); Thread consumer = new Consumer(); producer.setPriority(Thread.MIN_PRIORITY); //Min Priority consumer.setPriority(Thread.MAX_PRIORITY); //Max Priority producer.start(); consumer.start(); } } class Producer extends Thread { public void run() { for (int i = 0; i < 5; i++) { System.out.println("I am Producer : Produced Item " + i); Thread.yield(); } } } class Consumer extends Thread { public void run() { for (int i = 0; i < 5; i++) { System.out.println("I am Consumer : Consumed Item " + i); Thread.yield(); } } }
Output of above program “without” yield() method
I am Consumer : Consumed Item 0 I am Consumer : Consumed Item 1 I am Consumer : Consumed Item 2 I am Consumer : Consumed Item 3 I am Consumer : Consumed Item 4 I am Producer : Produced Item 0 I am Producer : Produced Item 1 I am Producer : Produced Item 2 I am Producer : Produced Item 3 I am Producer : Produced Item 4
Output of above program “with” yield() method added
I am Producer : Produced Item 0 I am Consumer : Consumed Item 0 I am Producer : Produced Item 1 I am Consumer : Consumed Item 1 I am Producer : Produced Item 2 I am Consumer : Consumed Item 2 I am Producer : Produced Item 3 I am Consumer : Consumed Item 3 I am Producer : Produced Item 4 I am Consumer : Consumed Item 4
join() method
The.
//Waits for this thread to die. public final void join() throws InterruptedException
Giving a timeout within join(), will make the join() effect to be nullified after the specific timeout. When the timeout is reached, the main thread and taskThread are equally probable candidates to execute. However, as with sleep, join is dependent on the OS for timing, so you should not assume that join will wait exactly as long as you specify.
Like sleep, join responds to an interrupt by exiting with an InterruptedException.
join() method example usage
package test.core.threads; public"); } }); Thread t1 = new Thread(new Runnable() { public void run() { System.out.println("Second task completed"); } }); t.start(); // Line 15 t.join(); // Line 16 t1.start(); } } Output: First task started Sleeping for 2 seconds First task completed Second task completed
That’s all for this quite small but important concept. Let me know of your thoughts in comments section.
Happy Learning !!
Feedback, Discussion and Comments
jitender
very good post for clearing concepts
Himansu
Hi Lokesh,
Just to add one imp point. If join() is called on a dead thread or thread which is not yet started than the control immediately return back without waiting.
Regards,
Himansu
Harsh Rastogi
You are saying that Yield method let other waiting threads to execute but if they are of same priority. In your example the producer and consumer are apparently of totally different priority.
How is yield affecting their execution order??
Lokesh Gupta
The comment you mentioned is for “thread pools”. In example, I have have not used thread pool.
Harsh Rastogi
Your reply is not clear. Are saying the yield only works for thread pool or the priority condition is associated with thread pool only?
It’ll be better if you could please explain it in detail for all of the readers.
Thanks!!
Lokesh Gupta
Yes Harsh, In thread-pool, yield() will try to suspend currently executing thread, and JVM will first try to choose a thread with equal priority inside pool, if none is found – it may choose the original thread or may choose any other thread of unequal priority.
Again, It is on best effort basis. This execution order is not guaranteed as most of the cases of the cases in multi-threading.
Yield method only suggest that current thread is ready to give up resources if some other thread want to take over. But JVM may choose to select that very thread everytime, irrespective of all reasoning. No guarantee at all.
saravanan
We have only runnable state which is running state. But line states they are two different.. Please clarify.
•It can only make a thread from Running State to Runnable State, not in wait or blocked state.
Lokesh
The thread is in runnable state after invocation of start() method, but the thread scheduler has not selected it to be the running thread. The thread is in running state if the thread scheduler has selected it. The thread is in running state if the thread scheduler has selected it.
Bittoo
HI lokesh,
Regarding join() method. Its written that “If join() is called on a Thread instance, the currently running thread will block until the Thread instance has finished executing”. Can you please explain this line in more detail whenever you get time :) . I am confused in the line “The currently running thread will block”.
As far as I understand its :
t.start();
t.join();
t1.start();
In the above case thread t will finish first then t1 will start.
If I write :
t.start();
t1.start();
t.join();
Both will be started and t.join() has no impact.
Is that mean that we have to call join on thread object just after calling start() method so that no other thread will start executing until our joined thread exits.
I know its a small doubt :) . please explain . Thanks in advance
Bittoo
Hi Lokesh,
I am getting the following output without yield :
I am Consumer : Consumed Item 0
I am Producer : Produced Item 0
I am Consumer : Consumed Item 1
I am Producer : Produced Item 1
I am Consumer : Consumed Item 2
I am Producer : Produced Item 2
I am Consumer : Consumed Item 3
I am Producer : Produced Item 3
I am Consumer : Consumed Item 4
I am Producer : Produced Item 4
and with yield() the output is :
I am Producer : Produced Item 0
I am Consumer : Consumed Item 0
I am Consumer : Consumed Item 1
I am Producer : Produced Item 1
I am Producer : Produced Item 2
I am Producer : Produced Item 3
I am Producer : Produced Item 4
I am Consumer : Consumed Item 2
I am Consumer : Consumed Item 3
I am Consumer : Consumed Item 4
I agree that in threading we can’t force the processor we only give request. But Why the output is opposite ??
Subrat Pandey
Hello Lokesh,
I am a regular reader of your blogs. Your articles are very comprehensive and easy to learn.
I was reading this article about Thread.Join(),
And , i feel the example used here is insufficient to explain Thread.join() and hence is a bit misleading.
When we use , t.join() , It is always the current thread which is put on waiting state till the tread ‘t’ finishes its processing.
In the above example , though there are 2 threads created viz -Thread t & Thread t1.
But when you do t.join() , None of the thread ,t or t1 are “joined” to each other.
It is the “main” (currently executing) thread which is joined(i.e. waiting) to thread ‘t’ .
So, main thread halts execution till thread ‘t’ does its Job.
Hence , there was no use of creating 2 threads , when they are not being “JOINED”.
I think a modified code could explain things better:”);
}
});
t.start(); // Line 15
t.join(); // Line 16
System.out.println(“Main finished”);
}
}
aditya
The thread priorities ranges varies from operating system to operating system. For windows it is 1-10, linux 1-5 and for solaris 1-127. Java API suggests use to use the constants MIN_PRIORITY and MAX_PRIORITY instead of directly providing the direct priority numbers.
Lokesh
True
Qian Xu
IMO, `yield` and `join` are totally two different things. No similarity at all.
Rinkesh
Following statement is misleading.
“Without yield(), though the output changes sometimes, but usually first all prouder lines are printed and then all consumer lines.”
It’s the other way my friend. Consumers are printed first and then producers as Consumers are having highest priority.
Lokesh
Yeh. It’s typo. I will correct it.
Suresh
Hey Lokesh I m getting some weired output as shown below :
Producing 0
Consuming 0
Consuming 1
Consuming 2
Consuming 3
Producing 1
Producing 2
Producing 3
Lokesh
No output should be considered as weird. In multi-threading, you can only ask the processor to give up a thread and execute other, you can’t force it.
Adarsha
Good article !
Gelin Luo
I tried the YieldExample many times on my laptop using “1.6.0_45”, I found the result is very randomly and it is almost not relevant to the yield statement
Lokesh
In multi-threading programs, results always vary so without yield() it’s quite expected. After using yield(), there must be some fixed ordering. Can you please post here, your outputs.
Gelin Luo
See
Lokesh
First two are similar outputs. Third is quite different. But it’s possible. Multi-threading does not guarantee a thing. | http://howtodoinjava.com/core-java/multi-threading/difference-between-yield-and-join-in-threads-in-java/ | CC-MAIN-2016-44 | refinedweb | 2,036 | 63.59 |
IRC log of tagmem on 2005-06-21
Timestamps are in UTC.
17:04:34 [RRSAgent]
RRSAgent has joined #tagmem
17:04:34 [RRSAgent]
logging to
17:04:42 [Norm]
title: TAG 21 June 2005 telcon
17:04:46 [Norm]
date: 21 June 2005
17:04:48 [Norm]
scribe: NW
17:04:51 [Norm]
scribenick: Norm
17:04:52 [Zakim]
+Dave_Orchard
17:05:05 [Norm]
zakim, who's here?
17:05:05 [Zakim]
On the phone I see Ed_Rice?, Norm, Ht, Vincent, Dave_Orchard
17:05:06 [Zakim]
On IRC I see RRSAgent, Vincent, Ed, dorchard, Zakim, Norm, noah, ht, DanC
17:05:15 [Norm]
regrets: Dan, Tim, Noah
17:05:24 [Norm]
absent: Roy
17:06:03 [Norm]
Telcon: 28 June?
17:06:05 [Norm]
Regrets: NW
17:06:11 [Norm]
Next telcon: 28 June 2005
17:06:34 [Norm]
Scribe will be Ed
17:07:52 [Norm]
topic: Approving minutes of the f2f
17:07:59 [Norm]
HT asks for time to review them
17:08:07 [Norm]
NW concurs
17:08:26 [Norm]
We'll approve the f2f minutes next week
17:09:55 [Norm]
topic: Technical discussion: TAG future directions
17:10:08 [Norm]
DC published summary at
17:11:25 [Norm]
subtopic: Grid Services
17:11:34 [ht]
HST would be happy to discuss his message to XML Schema about naming things if we have time
17:11:51 [Norm]
VQ: What seems interesting architecturally is the interaction of grid services with both web services and the semantic web
17:12:32 [Norm]
ht: My feeling is that there is an impact, but I don't know what it is
17:13:08 [Norm]
ht: I'd be happy to get educated in this area "on TAG time" as it were, if we could identify someone who has some reasonable understanding of the architecture of the grid and might be prepared to suggest some things we ought to look at
17:13:11 [Norm]
VQ: agreement
17:13:50 [Norm]
NW: Sun has some grid services work going; I can look for someone to come chat with us
17:14:20 [Norm]
ht: I have connections with ??? that I'll be giving a talk to about naming in ten days time. I'll look for interest there.
17:14:40 [ht]
UK National e-Science Centre
17:14:42 [Norm]
dorchard: I can do a limited job, or one of our distribued web management folks, there are a couple in our standards teams, that would be glad to talk about some of the work BEA has been lookin gat in this area
17:14:54 [Norm]
VQ: any other proposals?
17:15:32 [Norm]
VQ asks DO to give a brief intro
17:16:44 [Norm].
17:18:08 [ht]
HST understood the GRID to be something quite different from what DaveO is talking about
17:18:36 [Norm].);
17:18:56 [Norm]
VQ: This sounds very similar to web services.
17:19:19 [Norm]
VQ: Are you aware of the vision of the grid that is more about distributed computing, where resources are more like computing resources, CPU power, or data storage
17:20:00 [ht]
Global Grid Forum
17:20:06 [Norm]
dorchard: The term "grid" has many different meanings. I'm describing, briefly, one of those meanings. The output of the Open Grid Alliance (Forum?) ended up going this way.
17:20:22 [Norm]
s/Open Grid Alliance/Global Grid Forum/
17:20:37 [Norm]
DO: What I think we're going to have here are a few different views of what the grid and grid services mean
17:20:39 [ht]
I thought they had their own as-it-were rec-track. . .
17:20:59 [dorchard]
dorchard has joined #tagmem
17:21:05 [ht]
17:21:22 [Norm]
VQ: suggests going around the table to see if we're all on the same page
17:21:50 [Norm]
ht: From the particular corner of the intellectual space that I sit in, it's much more the scientific side that VQ mentioned.
17:22:38 [Norm]
ht: The focus seems to be sharing extremely high concentrations of computing power
17:23:07 [Norm]
ht: Problems like quantum chromodynamics and the calculations demanded by the superconducting supercollider
17:23:34 [Norm]
ht: This is simply more computing power than they can possibly have at one or two sites. It's in there general interest to make sure that everyone can get access to the available computing resources.
17:24:07 [Norm]
ht: there is a bunch of open source software out there for finding and integrating into the authentication model of the resources to "run jobs"
17:24:22 [Norm]
ht: they're also very interested in tracking the history of datasets.
17:24:23 [dorchard]
q+
17:24:43 [Vincent]
q?
17:24:55 [Vincent]
ack dorchard
17:25:21 [Norm]
dorchard: I think the area that people are seing from the WS side is the distinction of managing WS resources and using WS to manage resources
17:26:03 [Norm]
dorchard: Our customer base is concerned about managing computing resources on the order of thousands of resources
17:26:54 [Norm]
dorchard: Big customers need to be able to manage things like drive failure, manage devices, manage computers, etc. They want to have a big set of "things" avialable that they can take out when needed and to which they can add new devices.
17:27:11 [Norm]
dorchard: there's obvoius potential relationships between that view and the web view
17:27:28 [ht]
The GGF does indeed have a pub process, modelled on ours it looks like:
17:27:33 [Norm]
dorchard: points to ??? one of the authors of webdav. Formerly at BPEL. This is one possible starting place.
17:27:42 [Norm]
dorchard: can you fill in "???" for me, please
17:28:19 [Norm]
VQ asks NW about the grid
17:28:37 [dorchard]
s/???/Yaron Goland/g
17:28:38 [ht]
q+ to say that I'm more concerned to hear from further afield, i.e. the 'Big Physics' GRID as opposed to the WS-Grid
17:28:40 [dorchard]
17:28:58 [Norm]
NW: I really don't know more than the name. I think I've heard both sorts of discussions.
17:29:26 [Norm]
ER: We have a center inside HP that's working on Grid computing. I'd be happy to invite them if it isn't redundant.
17:30:06 [Norm]
VQ: We should try to find the right person to be invited first to give us an introduction to the grid
17:30:15 [Norm]
VQ asks HT about his connections
17:30:23 [Norm]
ht: I'll make some inquiries
17:30:46 [Norm]
ER: Suggests we each send a paragraph to the TAG outlining what our contacts are working on. As a way of figuring out who to ask.
17:31:42 [noah]
IBM is doing a lot of work on grid. Are you looking for experts who can orient us? If so, I can almost surely find someone good.
17:31:45 [Norm]
VQ: Sounds good, please send them.
17:32:42 [Norm]
NW: Noah seems to be indicating an ability to get someone as well.
17:32:54 [noah]
OK, I'll check in IBM. Are we looking for someone to dial into a TAG call? What's needed and what's the likely format?
17:33:37 [Norm]
We're just looking for a single para of intro so we can pick the right folks to invite
17:33:57 [Norm]
subtopic: P2P
17:34:14 [Norm]
NW points VQ to Noah's remark earlier
17:35:00 [Norm]
noah: Note that I think we covered P2P and streaming under schemeProtocols last week. The ball is in my court to propose next steps, I think.
17:36:32 [Norm]
VQ: I'm not sure the problems are all related directly to those areas. Noah has an action that's relevant, but I'm not sure that both issues are streaming and multimedia and P2P are all just scheme and protocol related
17:36:39 [Norm]
VQ: What other directions should we explore?
17:37:21 [Norm]
Scribe lost the beginning of that thread...
17:37:59 [Norm]
VQ: P2P and streaming could be related.
17:38:06 [Norm]
ER: I don't think P2P and streaming are really related
17:38:30 [Norm]
VQ: As far as protocols are concerned, they're using different protocols than the ones typically used on the web. Also, the way they carry information seems a bit different.
17:38:38 [Norm]
VQ: The notion of media type isn't handled the same way.
17:38:53 [Norm]
NW: So they aren't related to each other so much as they are both different from the typical web
17:39:12 [Norm]
VQ: Is the only issue related to web architecture the issue of schemes and protocols
17:40:13 [Norm]
NW: It seems to me that folks use P2P to get long streaming resources
17:41:04 [Norm]
17:41:59 [Norm]
dorchard: People are now trying to verify the representations that they actually obtain. This is an effort to heal the network's view of what the resource is. This treats the information space as if it was sort of local.
17:42:02 [Zakim]
+Noah_Mendelsohn
17:42:49 [Norm]
VQ: Asks Noah if he thinks there are other issues related to P2P and streaming
17:43:13 [Norm]
NM: I don't know and I certainly don't have any problem with discussing other issues. I just thought they were on the whiteboard at the f2f because of the stream/protocol stuff.
17:43:45 [Norm]
NM: I think the balls in my court to summarize the feedback that I got, both at the f2f and in email
17:44:02 [Norm]
dorchard: The thing I mentioned was the issue around retaining the state of the resource as it's distributed
17:44:45 [Norm]
dorchard: This is the security and distributed caching aspects I just talked about
17:46:11 [ht]
q+ to support the separation of the peer-to-peer question from schemesProtocols-??
17:46:15 [Norm].
17:47:03 [Norm]
VQ: In addition to the issue of schemes and protocols, it's not completely clear how to address the specific aspects of P2P and streaming. I'm not sure how to explore further to avoid missing other aspects of web architecture.
17:47:21 [Norm]
VQ: I don't see anything else to do in the short term.
17:47:30 [dorchard]
btw, the global grid URI that I see is
17:48:42 [Norm]
ht: Suggests that the schemes/protocols finding is a very general question, the question of, for instance, is it possible to integrate P2P transport mechanisms into the web, is perhaps a separate question and we should take it up in due course.
17:48:50 [Norm]
ht: I'd like to see that in a separate document, I think.
17:49:09 [ht]
ack
17:49:13 [ht]
ack ht
17:49:13 [Zakim]
ht, you wanted to say that I'm more concerned to hear from further afield, i.e. the 'Big Physics' GRID as opposed to the WS-Grid and to support the separation of the peer-to-peer
17:49:16 [Zakim]
... question from schemesProtocols-??
17:49:54 [Norm]
VQ suggests we proceed with the finding and if we discover that other issues are raised, then we can decide how to address them, perhaps separately.
17:49:55 [Zakim]
-Dave_Orchard
17:50:42 [Norm].
17:51:39 [Norm]
NM: If they're decoupled, we should separate them, but I'd like license to find out if they are.
17:51:41 [Norm]
ht: Of course
17:52:53 [Norm]
VQ asks NM about attendence
17:53:01 [Norm]
NM: I'll be here next week, then on vacation for two weeks
17:53:30 [Norm]
VQ: Several other folks are missing today. My proposal is to stop this discussion now and focus next week with NM on the scheme/protocol issues in more details
17:54:16 [Norm]
NM: That's fine, but I've had a lot of feedback so it may take time for me to get it all together
17:54:54 [Norm]
VQ: Any other issues?
17:55:12 [Norm]
ht: I'd welcome the opportunity to ask for some feedback about the naming discussion
17:55:28 [Norm]
ht: That's namespaceDocuments-8 and ...
17:55:38 [Zakim]
-Noah_Mendelsohn
17:56:12 [Norm]
ht: ... abstractComponentRefs-3x
17:56:26 [Norm]
ht: I'm writing a longer piece on this for the TAG to consider
17:56:53 [Norm]
ht: I think the point I'm starting from is that a change in the way we think about namespaces has slowly evolved
17:57:17 [Norm]
ht: It crystalized in the discussion about whether the XML Core WG had done a bad thing by "adding a new name to the XML namespace"
17:57:34 [Norm]
ht: After pushing that back and forth for a while, I think that position is incoherent
17:57:50 [Norm]
ht: The namespaces REC provides a disambiguation mechanism, it's a syntactic device. That's *it*
17:58:09 [Norm]
ht: In particular, the primary conceptual unit that emerges from the namespaces REC is that of "expanded name" (What QT calls "expanded-QName")
17:59:08 [Norm]
ht:
17:59:14 [Vincent]
q?
17:59:36 [Norm]
ht: it doesn't make any sense to talk about type definitions or graph nodes or information items being in a namespace. That's not the sort of thing a namespace is. A namespace is just shorthand for a namespace name.
17:59:50 [Norm]
NW: I think that's right.
18:00:37 [Norm]
ht: You didn't receive any feedback or answer to the message you sent yesterday evening?
18:00:41 [Norm]
s/ht:/vq:/
18:01:00 [Norm]
ht: No, but the user experience workshop is probably occupying some of the folks I'd have expected feedback from
18:01:02 [dorchard]
HT, I'm a little confused. Why can't we talk about adding a "new name to a namespace", when we say that a namespace *is defined by* a particular specification?
18:02:11 [Norm]
NW points out DO's comment and notes that DO is no longer on the phone
18:02:24 [Norm]
HT indicated his intent to reply in IRC for Dave
18:02:34 [ht]
Well, I don't think we should say that, rather that a spec assigns definitions to names which share a namespace name
18:03:08 [Norm]
VQ: Any other topics for today?
18:03:20 [DaveO]
DaveO has joined #tagmem
18:03:30 [Norm]
VQ: Adjourned
18:03:42 [Zakim]
-Ed_Rice?
18:03:43 [Zakim]
-Ht
18:03:45 [Zakim]
-Vincent
18:03:46 [Zakim]
-Norm
18:03:48 [Zakim]
TAG_Weekly()12:30PM has ended
18:03:49 [Zakim]
Attendees were +1.916.785.aaaa, Norm, Ht, [INRIA], Vincent, Dave_Orchard, Noah_Mendelsohn
18:04:01 [Norm]
rrsagent, pointer?
18:04:01 [RRSAgent]
See
18:04:02 [ht]
DaveO, I said Well, I don't think we should say that, rather that a spec assigns definitions to names which share a namespace name
18:04:09 [Norm]
rrsagent, make minutes public
18:04:09 [RRSAgent]
I'm logging. I don't understand 'make minutes public', Norm. Try /msg RRSAgent help
18:04:51 [Norm]
rrsagent, adminhelp
18:05:00 [Norm]
grrr, forgot to /msg that
18:05:11 [Norm]
rrsagent, make draft minutes
18:05:11 [RRSAgent]
I'm logging. I don't understand 'make draft minutes', Norm. Try /msg RRSAgent help
18:05:18 [Norm]
noah, do you remember the incantation?
18:05:40 [Norm]
oh, well, nevermind. I'll bang it together myself
18:05:44 [ht]
rrsagent, please convert minutes
18:05:44 [RRSAgent]
I'm logging. I don't understand 'please convert minutes', ht. Try /msg RRSAgent help
18:05:50 [ht]
rrsagent, please draft minutes
18:05:50 [RRSAgent]
I have made the request to generate
ht
18:05:53 [ht]
!
18:05:57 [Norm]
thank you!
18:06:05 [ht]
you have to use the magic word :-)
18:06:09 [Norm]
xyzzy!
18:06:11 [Norm]
plugh!
18:06:15 [ht]
LOL!
18:06:21 [Norm]
Hello sailor
18:06:41 [ht]
LOL again (fortunately everyone else within earshot has gone home by now)
18:06:50 [Norm]
heh
18:06:54 [Norm]
Night ht!
18:07:07 [ht]
night, thanks for scribing
18:07:22 [ht]
Nice to be home for an extended period, yes?
18:12:10 [Norm]
Yes!
20:15:13 [Zakim]
Zakim has left #tagmem
20:53:32 [Norm]
Norm has joined #tagmem
22:04:43 [noah_Schema_mtg]
noah_Schema_mtg has joined #tagmem | http://www.w3.org/2005/06/21-tagmem-irc | CC-MAIN-2016-50 | refinedweb | 2,843 | 73.61 |
Unit
Testing
with
Python
Materials available at:
Overview
- What is unit testing
- Why do unit testing
- Python crash course
- How to do unit testing in Python
What is Unit Testing?
- Goal: Isolate a unit of code and test its' correctness
- Test it through using it in a "test" method and by asserting some behavior to be true
- By testing every unit you can ensure that the whole program is correct
- These tests can be automated or manual
- Tests are executed often to ensure the code is working
Good Unit Tests
- Short and sweet
- Quick execution
- One desired functionality per test
- Cover all of the code
- Contain good code
- Including readability and best practices
- Have explicit method names
Why bother with Unit Testing?
- You can ensure that future changes do not break the existing functionality
- Easier to find where the code is wrong
- If you write the unit tests first it often simplifies development, this is called Test Driven Development
Python Crash Course
REPL
Read - Evaluate - Print - Loop
Python 3.7.2+ (default, Feb 27 2019, 15:41:59) [GCC 8.2.0] on linux Type "help", "copyright", "credits" or "license" for more information. >>> print("Hello, world!") Hello, world!
Functions
def foo(argument_1, argument_2): return argument_1 + argument_2 >>> foo(1, 2) 3
Conditionals
if number == 1: print("one") elif number == 2: print("two") elif number == 3: print("three")
Classes
class Jody: def __init__(self, love_for_gryffn): self.has_dog = True self.love_for_dog = love_for_gryffn def grade_homework(self, grade): if grade > 90: return "A" else: return "F" >>> strausser = Jody(10000) >>> strausser.grade_homework(101) "A"
Imports
import math >>> print(math.log(10)) 2.302585092994046
How to Unit Test in Python 3
- UnitTest
- DocTest
- Quick and dirty way of doing unit tests
- Searches for REPL-like blocks in the comment at the top of a function
- ut-doctest.py
- "Classic" way of doing unit tests
- Create a new class containing functions that do the tests
- ut-unittest.py
Additional Resources
- To learn Python:
- To learn more about testing in Python:
Unit Testing with Python
By Alex Day
Unit Testing with Python
Introduction to unit testing with python in mind | https://slides.com/alexday-2/unit-testing-with-python | CC-MAIN-2021-31 | refinedweb | 351 | 52.63 |
Advertisement
hai .......Ajay Anand,
I am krishna.
using get
hai .......Ajay Anand,
I am krishna.
using getParamater() in HttpRequestServelt in servelt.
u can retrive the data from html form to ActionServet.
Example:
========
<input name=text
Servelt:
=========
import javax.servlet.
How to retrive values from an html file through se
How to retrive values from an html file through servlet.Mainly of the combobox.
friendly teaching
Extrimly Good
question
i would like to ask how to remove space when getting parameters. for example
java peoples are kings
java peoples are kings
Well Explained
This is a very good explanation. thank you for your hel
Comment
Great!!!
It was easier to understand as it has some exam code. Explanation is also good.
Thnx
This site was very useful for me..An excellent example to understand Request objects
hai
hai I am using windows 7 with 32 bit os
I installed java 1.6 version
I also installed oracle 10g.
When I am trying to execute
jdbc-odbc programs... with the java code using driver "sun.jdbc.odbc.JdbcOdbcDriver", then follow these steps:
1
hai
hai how to get chechbox in web page using jsp
Hi Friend...("lang");
out.println("You have selected:");
for(int i=0;i<st.length;i++){
out.println(st[i]);
}
}
%>
Thanks
ajay
ajay can anyone tell me how intrusion detection system works.
and how it can be developed by using java
ajay
ajay can i use hibernate in javafx ? please give one sample application
Anand | http://roseindia.net/tutorialhelp/allcomments/1769 | CC-MAIN-2015-22 | refinedweb | 247 | 69.99 |
Troubleshoot a Classic Load Balancer: HTTP Errors
The HTTP method (also called the verb) specifies the action to be performed on the resource receiving an HTTP request. The standard methods for HTTP requests are defined in RFC 2616, Method Definitions. The standard methods include GET, POST, PUT, HEAD, and OPTIONS. Some web applications require (and sometimes introduce) methods that are extensions of HTTP/1.1 methods. Common examples of HTTP extended methods include PATCH, REPORT, MKCOL, PROPFIND, MOVE, and LOCK. Elastic Load Balancing accepts all standard and non-standard HTTP methods.
HTTP requests and responses use header fields to send information about the HTTP messages. Header fields are colon-separated name-value pairs that are separated by a cariage return (CR) and a line feed (LF). A standard set of HTTP header fields is definied in RFC 2616, Message Headers. For more information, see HTTP Headers and Classic Load Balancers.. If the length of the method in the request exceeds 127 characters, the load balancer responds with an HTTP 405: METHOD_NOT_ALLOWED error.
The EC2 instance processes a valid request by implementing the method in the request and sending a response back to the client. Your instances must be configured to handle both supported and unsupported methods.
The following are error messages returned by your load balancer, the potential causes, and the steps you can take to resolve the issues.
Error Messages
HTTP 400: BAD_REQUEST
Description: Indicates that the client sent a bad request.
Cause: The client sent a malformed request that does not meet HTTP specifications. For example, a request can't have spaces in the URL.
Solution: Connect directly to your instance and capture the details of the client request. Review the headers and the URL for malformed requests. Verify that the request meets HTTP specifications.
HTTP 405: METHOD_NOT_ALLOWED
Description: Indicates that the method length is not valid.
Cause: The length of the method in the request header exceeds 127 characters.
Solution: Check the length of the method.
HTTP 408: Request Timeout
Description: Indicates that the client cancelled the request or failed to send a full request.
Cause 1: A network interruption or a bad request construction, such as partially formed headers; specified content size doesn't match the actual content size transmitted; and so on.
Solution 1: Inspect the code that is making the request and try sending it directly to your registered instances (or a development / test environment) where you have more control over inspecting the actual request.
Cause 2: Connection to the client is closed (load balancer could not send a response)
Solution 2: Verify that the client is not closing the connection before a response is sent by using a packet sniffer on the machine making the request.
HTTP 502: Bad Gateway
Description: Indicates that the load balancer was unable to parse the response sent from a registered instance.
Cause: Malformed response from the instance or potentially an issue with the load balancer.
Solution: Verify that the response being sent from the instance conforms to HTTP specifications. Go to the AWS Support Center for assistance.
HTTP 503: Service Unavailable
Description: Indicates that either the load balancer or the registered instances are causing the error.
Cause 1: Insufficient capacity in the load balancer to handle the request.
Solution 1: This should be a transient issue and should not last more than a few minutes. If it persists, go to the AWS Support Center for assistance.
Cause 2: No registered instances.
Solution 2: Register at least one instance in every
Availability Zone that your load balancer is configured to respond in.
Verify this by looking at the
HealthyHostCount metrics in
CloudWatch. If you can't ensure that an instance is registered in each
Availability Zone, we recommend enabling cross-zone load balancing. For more
information, see Configure Cross-Zone Load Balancing for Your Classic Load Balancer.
Cause 3: No healthy instances.
Solution 3: Ensure that you have healthy instances
in every Availability Zone that your load balancer is configured to respond
in. Verify this by looking at the
HealthyHostCount in CloudWatch.
HTTP 504: Gateway Timeout
Description: Indicates that the load balancer closed a connection because a request did not complete within the idle timeout period.
Cause 1: The application takes longer to respond than the configured idle timeout.
Solution 1: Monitor the
HTTPCode_ELB_5XX and
Latency metrics. If there is an increase in these metrics, it could be due to
the application not responding within the idle timeout period. For details about the requests
that are timing out, enable access logs on the load balancer and review the 504 response codes
in the logs that are generated by Elastic Load Balancing. If necessary, you can increase your capacity or increase
the configured idle timeout so that lengthy operations (such as uploading a large file) can complete.
For more information, see Configure the Idle Connection Timeout for Your Classic Load Balancer
and How do I troubleshoot Elastic Load Balancing high latency.
Cause 2: Registered instances closing the connection to Elastic Load Balancing.
Solution 2: Enable keep-alive settings on your EC2 instances and make sure that the keep-alive timeout is greater than the idle timeout settings of your load balancer. | http://docs.aws.amazon.com/elasticloadbalancing/latest/classic/ts-elb-error-message.html | CC-MAIN-2017-13 | refinedweb | 862 | 54.93 |
Bug #10552
Partitionable glideins not accounted for correctly - not accounted for at all
0%
Description
This is a follow-up of issue #6897 that did not solve the problem.
Mats pointed out that the problem was not resolved and helped to identify it better:
1. the names in condor_status/Name include the partition id (e.g. slot1_2@...)
slot1@glidein_31618_384461100@uct2-c161.mwt2.org
slot1_1@glidein_31618_384461100@uct2-c161.mwt2.org
slot1_3@glidein_31618_384461100@uct2-c161.mwt2.org
slot1_4@glidein_31618_384461100@uct2-c161.mwt2.org
2. the names in condor_q/RemoteHost have only the slot (e.g. slot1@…)
3 slot1@glidein_31618_384461100@uct2-c161.mwt2.org
3. appendRealRunning in glideinFrontendLib.py is looking for a match (the dictionary key is the name from condor_status):
condor_status = status_dict[collector_name].fetchStored()
if remote_host in condor_status:
….
and is called with:
glideinFrontendLib.appendRealRunning(self.condorq_dict_running,
self.status_dict_types['Running']['dict'])
The parent slot (slot1@…) is not running any job, so it is not in the list (otherwise the number of running glideins would be incorrect), therefore is not matched in appendRealRunning and is not counted.
Now I don’t know which is the correct path to solve this problem:
1. the job should report the exact slot in which it runs and this is a HTCondor bug
2. the job is reporting only the parent slot and GWMS should parse the collector entry to match with the parent slot name
My preference would be for solution 1 if possible.
Solution 2 can be done within the gwms code but works only if the jobs in the sub-slots are equivalents because there is no easy way to match the job with the correct sub-slot (I watched inside the ClassAds and I think the only way to match is via PublicClaimId that I don't think it is saved in the dictionaries - those would need to be changed as well).
History
#1 Updated by Marco Mambelli over 4 years ago
- File 0001-matching-the-main-slot-for-partitionable-slots.patch 0001-matching-the-main-slot-for-partitionable-slots.patch added
Since GLIDEIN_Schedd, GLIDEIN_Entry_Name, GLIDEIN_Name and GLIDEIN_Factory depend on the submission and are all the same for sub-slots of a partitionable glidein, then solution 2 is possible.
It is in branch v3/10552 and attached in patch
#2 Updated by Parag Mhashilkar over 4 years ago
- Target version set to v3_2_12
#3 Updated by Parag Mhashilkar over 4 years ago
- Target version changed from v3_2_12 to v3_2_13
#4 Updated by Burt Holzman over 4 years ago
Hi Marco - this is what I just e-mail about, didn't know you had a bug already created for it.
I don't think #1 is the answer - HTCondor has always reported the parent slot as RemoteHost.
Isn't it trivial to match RemoteHost with the machine Name since we know the form is slotX_Y?
#5 Updated by Marco Mambelli over 4 years ago
In the meeting with the condor team on 12/11 Zach and Todd explained how dynamic slots are created only for the match of the job (existing only when claimed) so is preferable to use the parent partitionable slot for RemoteHost. There may be in the future a new attribute added to the job to track the actual slot.
This means that option #1 is not viable.
#6 Updated by Marco Mambelli over 4 years ago
- Status changed from New to Feedback
- Assignee changed from Marco Mambelli to Burt Holzman
- Target version changed from v3_2_13 to v3_2_12
New changes are in v3/10552_v2, ignore the changes in v3/10552
In this version partitionable glideins are counted as 1 for total, as 1 running glidein if there is at least one dynamic slot, as 1 idle glidein if they have enough cpu and memory (cpu>0 and memory>2500MB, these limits have been imposed by CMS)
Note that sometime idle+running != total (partitionable glideins may be counted as both running and idle)
Are the conditions in the selection and in the count are OK and are not slowing down too much?
#7 Updated by Marco Mambelli over 4 years ago
- Assignee changed from Burt Holzman to HyunWoo Kim
#8 Updated by HyunWoo Kim over 4 years ago
- Status changed from Feedback to Assigned
- Assignee changed from HyunWoo Kim to Marco Mambelli
I reviewed the 2 files that have changed
and there are two comments from me, see below..
1. frontend/glideinFrontendElement.py
only the changes as countCoresCondorStatus has changed its signature.
2. frontend/glideinFrontendLib.py
def getIdleCondorStatus
one change in the use of dictionary get method
Suggestion> one comment is, in line # 585, there is a comment line, # None != True, no need to set default
Shouldn't this go above line # 585?
def getRunningConderStatus
improvement in the logic
def getFailedCondorStatus
just lines and indentations
def getIdleCoresCondorStatus
removed the redundant method body and redirected to getIdleCondorStatus
Suggestion> the comments for this method might be a bit obsolete now,
Why don't we explain in more details, why and how these two methods, getIdleCoresCondorStatus and getIdleCondorStatus
have the same logic? and thus that the redundant part has been removed and that this method is redirected to getIdleCondorStatus..
def countCoresCondorStatus
added second argument to cover TotalCores, IdleCores, RunningCores
#9 Updated by Marco Mambelli over 4 years ago
- Status changed from Assigned to Resolved
#10 Updated by Parag Mhashilkar over 4 years ago
- Status changed from Resolved to Closed
Also available in: Atom PDF | https://cdcvs.fnal.gov/redmine/issues/10552 | CC-MAIN-2020-29 | refinedweb | 899 | 53.04 |
Version 0.10 has been released two and a half months after 0.9, bringing many new features and enhancements. The second issue of Elvish Newsletter accompanies this release.
Breaking changes
If you are upgrading from an earlier version, Elvish will complain that your database is not valid. This is because Elvish now uses BoltDB for storage. A database migration tool is available.
Breaking changes to the editor API:
The
$edit:completermap is now known as
$edit:arg-completer.
The keybinding API has been changed (again). Keybindings for different now live in their own subnamespaces. For instance, keybindings for insert mode used to be
edit:binding[insert]but is now
edit:insert:binding.
Module names of some editor modes have also been changed for consistency. The completion mode now uses the
edit:completionmodule (used to be
edit:compl). Location mode:
edit:location; navigation mode:
edit:navigation.
Byte output from prompts now preserve newlines. For instance, if you have
edit:prompt = { echo haha }, you will now have a trailing newline in the prompt, making your command appear on the next line. To fix this, simple replace
echowith
Breaking changes to the language core:
Due to the switch to persistent data structures, assignments of maps now behave as if they copy the entire container. See the section in some unique semantics for an explanation.
The implicit
$argsvariable is gone, as well as its friends: positional variables
$0,
$1, …, and the special
$@shorthand for
$@args. Lambdas defined without argument list (
{ some code }) now behave as if they have an empty argument list. (#397)
Old lambdas that rely on
$argsor its friends now must declare their arguments explicitly. For instance,
fn ls { e:ls --color=auto $@ }needs to be rewritten to
fn ls [@a]{ e:ls --color=auto $@a }.
Support for using backquotes for output capture (e.g.
echo uname is `uname`) has been removed. Use parentheses instead (e.g.
echo uname is (uname)).
Backquotes are repurposed for line continuation. A backquote followed by a newline is equivalent to a space. (#417)
The signature of the
splitsbuiltin has been changed. The separator used to be an option
sepbut is now the first argument. For instance,
splits &sep=: a:b:cshould now be written as
splits : a:b:c.
Notable fixes and enhancements
Thanks to the BoltDB migration, Elvish is now a pure Go project! This allows for fully statically linked executables and easy cross compilation. (#377)
Enhancements to the language core:
New builtins functions and variables (documented in the builtin module reference):
New
assocand
dissocbuiltin that outputs modified versions of container types.
New
keys,
has-keysand
has-valuesbuiltins (#432, #398, #407).
A new blackhole variable
$_has been added. (#401)
New
replacesbuiltin for replacing strings. (#463)
New
not-eqbuiltin for inequality.
New
dropbuiltin, mirroring
take.
Enhancements to the editor:
Matching algorithm used in completion is now programmable with
$edit:-matcher(#430); see documentation.
Elvish can now able to complete arguments with variables. For instance, if you have a directory with
a.mp4and
a.txt, and variable
$foocontaining
a,
echo $foo.<Tab>now works (#446). However, the completion will expand
$foointo
a, which is not intended (#474).
It is now possible to manipulate the cursor position using the experimental
$edit:-dotvariable (415).
The default prompt now replaces
>with a red
#when uid = 0.
An experimental custom listing mode (known as “narrow mode” for now) has been introduced and can be started with
edit:-narrow-read. This means that it is now to implement listing modes entirely in Elvish script.
Experimental re-implementations of the several standard listing modes (location mode, history lising mode and lastcmd mode) are provided as the bundled
narrowmodule. Read its source in eval/narrow.elv for more details.
Improvements to the daemon:
Elvish no longer quits on SIGQUIT (usually triggered by
Ctrl-\), matching the behavior of other shells. It still prints a stack trace though, which can be useful for debugging. (#411)
A
-compileonlyflag for the Elvish binary is added. It makes Elvish compiles a script (in memory) but does not execute it. It can be used for checking the well-formedness of programs and is useful in editor plugins. (#458) | https://elv.sh/blog/0.10-release-notes.html | CC-MAIN-2018-51 | refinedweb | 689 | 59.7 |
Following the documentation, I tried to implement an action with an executable script:
tailf:action myaction {
tailf:exec "/tmp/myaction.py";
description
"my action";
// input;
output {
leaf var1 {
description
"Some string";
type string;
}
leaf var2 {
description
"Some other variable";
type string;
}
}
}
Compilation works, but when in confd_cli, I always get an error with no details:
request myroot myactionError: [error][2017-10-06 08:37:20]
The script is never run, even though it has executable privileges for all users.
I tried replacing the python script with a bash script, but had the same result. The empty error message doesn't help much.
What did I miss?
What does the developer log say?
Nothing at all...
I had a look at the manual of confd.conf, I set up <developerLogLevel>trace</developerLogLevel>, confdLog is enabled on file, and so are developerLog and errorLog.
<developerLogLevel>trace</developerLogLevel>
They don't show anything relevant to my error...
I also tried launching confd with confd --verbose --foreground, but no luck.
Sure it will. The developer log will show that your osCommand produced an error when it was executed.And so now it is up to you to debug that error in your script from your command line for example.
Here is a quick example as a reference:
$ pwd
/Users/tailf/py_action
$ ls
Makefile confd.conf config.yang ping.py
$ cat config.yang
module config {
namespace "";
prefix config;
import tailf-common {
prefix tailf;
}
container config {
list host {
key name;
leaf name {
type string;
}
tailf:action ping {
tailf:exec "./ping.py" {
tailf:args "-c $(context) -p $(path)";
tailf:wd ".";
}
input {
leaf count {
type int32;
mandatory false;
default "3";
}
}
output {
leaf result {
type string;
}
}
}
}
}
}
$ cat ping.py
#!/usr/bin/env python
import sys
import os
x,y,host = sys.argv[4].split()
if (len(sys.argv) == 7):
count = sys.argv[6]
else:
count = "1"
str = "ping -c %s %s"%(count, host)
result = os.popen(str).read()
print """result '
Invoked from %s
Ping to %s count %s:
%s'"""%(sys.argv[2], host, count, result)
$ make all start
...
$ confd_cli -u admin
admin connected from 127.0.0.1 using console
# config
(config)# config host localhost
(config)# commit
Commit complete.
(config)# do config host localhost ping count 1
result
Invoked from cli
Ping to localhost count 1:
PING localhost (127.0.0.1): 56 data bytes
64 bytes from 127.0.0.1: icmp_seq=0 ttl=64 time=0.045 ms
--- localhost ping statistics ---
1 packets transmitted, 1 packets received, 0.0% packet loss
round-trip min/avg/max/stddev = 0.045/0.045/0.045/0.000 ms
Thanks. The problem is not inside my script, which executes without any errors if run. It's confd that does not run the script at all.
I try to run the action via confd_cli and always get the blank error message described in my first message.
I tried:- moving the executable script to /tmp, giving full access to it to all users- enabling all logs in confd.conf- enabling the 'trace' log level
No luck...
So, what is the output, and the exit code (do 'echo $?' in the shell immediately after running it), of your script?
My script logs to a file as soon as it's called and takes 20-30 seconds to finish its execution. It really seems that confd cannot even find the script, even if I specify it by its absolute path and make it executable by all users.
# /path/to/my/script/myscript.py
output1 'some string'
output2 'some other string'
# echo $?
0
# ll /path/to/my/script/myscript.py
-rwxr-xr-x 1 root root 9039 Oct 9 16:19 /path/to/my/script/myscript.py
Well, the output parameters output1/output2 don't match the var1/var2 that you had in your YANG snippet, but that doesn't explain the empty error and the script not being run at all... But maybe there are other differences - are you sure that you are updating, re-compiling, and restarting ConfD with, the right version of the module when you make changes? Can you run the 'ping' action in the intro/7-c_actions example? When I change the path in the YANG module there, I get the expected error in the CLI:
admin@mars% set config host localhost
[ok][2017-10-09 18:44:48]
[edit]
admin@mars% request config host localhost ping count 1
Error: /nowhere/ping.pl: No such file or directory
[error][2017-10-09 18:45:01]
Yeah, I wrote output1/output2 on the spot, replacing my real variables. Hence the mismatch
Anyways, I copied and pasted the ping example into my yang file, and I get the same blank error message as with my code.
Can it be a permission problem? How do I declare that a given user or user group can execute actions?
I update the model and restart confd properly. The prompt on confd_cli correctly autocompletes with the name of the action I want to perform.
What's even more weird is that I just tried to run the action via netconf and I got "unknown element" error...
I think it would be better if you actually (if possible) ran the example, to reduce the number of unknowns... I wonder if there is something wrong with your ConfD installation - tailf:exec actions are run via the program $CONFD_DIR/lib/confd/lib/core/confd/priv/cmdwrapper - does it exist and is executable?
There is nothing that needs to be "declared" for that. You can control it via the AAA/NACM rules just like everything else, but the defaults should not prevent running actions (and those rules don't differentiate between action-as-callback and action-as-executable).
What exactly was the "unknown element" (this should be inciuded in the info)? It might just be that you need to set /confdConfig/netconf/capabilities/actions/enabled to "true".
That was the way to go. With the help of strace, I looked at the system calls that are executed when I run my action and it turned out that I didn't have the file child_setup in my installation of Confd.
Works like a charm now! Thanks a lot! | http://discuss.tail-f.com/t/tailf-exec-not-launching-anything/1580 | CC-MAIN-2018-09 | refinedweb | 1,026 | 66.23 |
Python Extension Programming with C
Any code that you write using any compiled language like C, C++ or Java can be integrated or imported into another Python script. This code is considered as an "extension."
A Python extension module is nothing more than a normal C library. On Unix machines, these libraries usually end in .so (for shared object). On Windows machines, you typically see .dll (for dynamically linked library).
Pre-Requisite:
To start writing your extension, you are going to need the Python header files.
On Unix machines, this usually requires installing a developer-specific package such as python2.5-dev.
Windows users get these headers as part of the package when they use the binary Python installer.
Additionally, it is assumed that you have good knowledge of C or C++ to write any Python Extension using C programming.
First look at a Python extension:
For your first look at a Python extension module, you'll be grouping your code into four parts:
The header file Python.h.
The C functions you want to expose as the interface from your module.
A table mapping the names of your functions as Python developers will see them to C functions inside the extension module.
An initialization function.
The header file Python.h
Start including Python.h header file in your C source file, which will give you access to the internal Python API used to hook your module into the interpreter.
Be sure to include Python.h before any other headers you might need. You'll follow the includes with the functions you want to call from Python.
The C functions:
The signatures of the C implementations of your functions will always take one of the following three forms:
static PyObject *MyFunction( PyObject *self, PyObject *args ); static PyObject *MyFunctionWithKeywords(PyObject *self, PyObject *args, PyObject *kw); static PyObject *MyFunctionWithNoArgs( PyObject *self );
Each one of the preceding declarations returns a Python object. There's no such thing as a void function in Python as there is in C. If you don't want your functions to return a value, return the C equivalent of Python's None value. The Python headers define a macro, Py_RETURN_NONE, that does this for us.
The names of your C functions can be whatever you like as they will never be seen outside of the extension module. So they would be defined as static function.
Your C functions usually are named by combining the Python module and function names together, as shown here:
static PyObject *module_func(PyObject *self, PyObject *args) { /* Do your stuff here. */ Py_RETURN_NONE; }
This would be a Python function called func inside of the module module. You'll be putting pointers to your C functions into the method table for the module that usually comes next in your source code.
The method mapping table:
This method table is a simple array of PyMethodDef structures. That structure looks something like this:
struct PyMethodDef { char *ml_name; PyCFunction ml_meth; int ml_flags; char *ml_doc; };
Here is the description of the members of this structure:
ml_name: This is the name of the function as the Python interpreter will present it when it is used in Python programs.
ml_meth: This must be the address to a function that has any one of the signatures described in previous seection.
ml_flags: This tells the interpreter which of the three signatures ml_meth is using.
This flag will usually have a value of METH_VARARGS.
This flag can be bitwise or'ed with METH_KEYWORDS if you want to allow keyword arguments into your function.
This can also have a value of METH_NOARGS that indicates you don't want to accept any arguments.
ml_doc: This is the docstring for the function, which could be NULL if you don't feel like writing one
This table needs to be terminated with a sentinel that consists of NULL and 0 values for the appropriate members.
Example:
For the above-defined function, we would have following method mapping table:
static PyMethodDef module_methods[] = { { "func", (PyCFunction)module_func, METH_NOARGS, NULL }, { NULL, NULL, 0, NULL } };
The initialization function:
The last part of your extension module is the initialization function. This function is called by the Python interpreter when the module is loaded. It's required that the function be named initModule, where Module is the name of the module.
The initialization function needs to be exported from the library you'll be building. The Python headers define PyMODINIT_FUNC to include the appropriate incantations for that to happen for the particular environment in which we're compiling. All you have to do is use it when defining the function.
Your C initialization function generally has the following overall structure:
PyMODINIT_FUNC initModule() { Py_InitModule3(func, module_methods, "docstring..."); }
Here is the description of Py_InitModule3 function:
func: This is the function to be exported.
module_methods: This is the mapping table name defined above.
docstring: This is the comment you want to give in your extension.
Putting this all together looks like the following:
#include <Python.h> static PyObject *module_func(PyObject *self, PyObject *args) { /* Do your stuff here. */ Py_RETURN_NONE; } static PyMethodDef module_methods[] = { { "func", (PyCFunction)module_func, METH_NOARGS, NULL }, { NULL, NULL, 0, NULL } }; PyMODINIT_FUNC initModule() { Py_InitModule3(func, module_methods, "docstring..."); }
Example:
A simple example that makes use of all the above concepts:
#include <Python.h> static PyObject* helloworld(PyObject* self) { return Py_BuildValue("s", "Hello, Python extensions!!"); } static char helloworld_docs[] = "helloworld( ): Any message you want to put here!!\n"; static PyMethodDef helloworld_funcs[] = { {"helloworld", (PyCFunction)helloworld, METH_NOARGS, helloworld_docs}, {NULL} }; void inithelloworld(void) { Py_InitModule3("helloworld", helloworld_funcs, "Extension module example!"); }
Here the Py_BuildValue function is used to build a Python value. Save above code in hello.c file. We would see how to compile and install this module to be called from Python script.
Building and Installing Extensions:
The distutils package makes it very easy to distribute Python modules, both pure Python and extension modules, in a standard way. Modules are distributed in source form and built and installed via a setup script usually called setup.py as follows.
For the above module, you would have to prepare following setup.py script:
from distutils.core import setup, Extension setup(name='helloworld', version='1.0', \ ext_modules=[Extension('helloworld', ['hello.c'])])
Now, use the following command, which would perform all needed compilation and linking steps, with the right compiler and linker commands and flags, and copies the resulting dynamic library into an appropriate directory:
$ python setup.py install
On Unix-based systems, you'll most likely need to run this command as root in order to have permissions to write to the site-packages directory. This usually isn't a problem on Windows
Import Extensions:
Once you installed your extension, you would be able to import and call that extension in your Python script as follows:
#!/usr/bin/python import helloworld print helloworld.helloworld()
This would produce the following result:
Hello, Python extensions!!
Passing Function Parameters:
Because you'll most likely want to define functions that do accept arguments, you can use one of the other signatures for your C functions. For example, following function, that accepts some number of parameters, would be defined like this:
static PyObject *module_func(PyObject *self, PyObject *args) { /* Parse args and do something interesting here. */ Py_RETURN_NONE; }
The method table containing an entry for the new function would look like this:
static PyMethodDef module_methods[] = { { "func", (PyCFunction)module_func, METH_NOARGS, NULL }, { "func", module_func, METH_VARARGS, NULL }, { NULL, NULL, 0, NULL } };
You can use API PyArg_ParseTuple function to extract the arguments from the one PyObject pointer passed into your C function.
The first argument to PyArg_ParseTuple is the args argument. This is the object you'll be parsing. The second argument is a format string describing the arguments as you expect them to appear. Each argument is represented by one or more characters in the format string as follows.
static PyObject *module_func(PyObject *self, PyObject *args) { int i; double d; char *s; if (!PyArg_ParseTuple(args, "ids", &i, &d, &s)) { return NULL; } /* Do something interesting here. */ Py_RETURN_NONE; }
Compiling the new version of your module and importing it will enable you to invoke the new function with any number of arguments of any type:
module.func(1, s="three", d=2.0) module.func(i=1, d=2.0, s="three") module.func(s="three", d=2.0, i=1)
You can probably come up with even more variations.
The PyArg_ParseTuple Function:
Here is the standard signature for PyArg_ParseTuple function:
int PyArg_ParseTuple(PyObject* tuple,char* format,...)
This function returns 0 for errors, and a value not equal to 0 for success. tuple is the PyObject* that was the C function's second argument. Here format is a C string that describes mandatory and optional arguments.
Here is a list of format codes for PyArg_ParseTuple function:
Returning Values:
Py_BuildValue takes in a format string much like PyArg_ParseTuple does. Instead of passing in the addresses of the values you're building, you pass in the actual values. Here's an example showing how to implement an add function:
static PyObject *foo_add(PyObject *self, PyObject *args) { int a; int b; if (!PyArg_ParseTuple(args, "ii", &a, &b)) { return NULL; } return Py_BuildValue("i", a + b); }
This is what it would look like if implemented in Python:
def add(a, b): return (a + b)
You can return two values from your function as follows, this would be cauptured using a list in Python.
static PyObject *foo_add_subtract(PyObject *self, PyObject *args) { int a; int b; if (!PyArg_ParseTuple(args, "ii", &a, &b)) { return NULL; } return Py_BuildValue("ii", a + b, a - b); }
This is what it would look like if implemented in Python:
def add_subtract(a, b): return (a + b, a - b)
The Py_BuildValue Function:
Here is the standard signature for Py_BuildValue function:
PyObject* Py_BuildValue(char* format,...)
Here format is a C string that describes the Python object to build. The following arguments of Py_BuildValue are C values from which the result is built. The PyObject* result is a new reference.
Following table lists the commonly used code strings, of which zero or more are joined into string format.
Code {...} builds dictionaries from an even number of C values, alternately keys and values. For example, Py_BuildValue("{issi}",23,"zig","zag",42) returns a dictionary like Python's {23:'zig','zag':42}. | http://www.tutorialspoint.com/python/python_further_extensions.htm | CC-MAIN-2014-15 | refinedweb | 1,690 | 55.13 |
Frank Rice
Microsoft Corporation
February 2005
Applies to:
Microsoft Office Excel 2003
Summary: Learn the rules and instances where Microsoft Office Excel 2003 infers schema from XML data during import and export. Understand why Excel creates the schemas it does and learn to modify your own XML data to create a schema that fits your needs. (6 printed pages)
Introduction General Rules Rules Applying to Double-Byte Numbers How Excel Handles XSD Data Types Unsupported XML Schema Constructs XSD Processing Rules Exceptions to Processing Rules Effect of Multiple Namespaces on Importing and Exporting XML Data Conclusion Additional Resources
You can import and export XML data into Microsoft Office Excel 2003. In both cases, you can use a schema (XSD) file to define the structure of the resulting file. However, when no schema is explicitly stated during these operations, Excel creates or infers one. This article reviews the rules and what is inferred in a specific instance of XML data.
The following rules are applicable when importing and exporting XML data to Excel.
xsi:nil="true"
Excel only infers a numeric data type for an element when all of the characters in the data for that element are XSD numeric characters. That means that double-byte numbers are inferred as String data type (see the exception noted below). Double-byte numbers provide support for many different East Asian language alphabets, such as Chinese, Japanese, and Korean. ASCII characters are only one byte in length, whereas Japanese, Korean, and other East Asian characters are two bytes in length.
In Extended ASCII (EA) Mode (InstallLanguage = JPN, KOR, CHS, CHT), Excel converts double-byte numbers imported or entered into the grid to numbers. In non-EA Mode, Excel treats double-byte numbers as strings.
The following table lists the XSD data types and describes how Excel handles them:
Table 1. XSD data types
INF – infinity; NaN – Not a number. Each of these have a binary representation in Excel. The XML Mapper converts INF and NaN to binary, and passes that to Excel, and converts it back during export. Excel displays as much of the number as the cell width allows.
If the data element contains only ones and zeros Boolean is not inferred. If the data element contains only True or False, with optional ones and zeros, Boolean is inferred.
Excel format: H:MM:SS
Fractional seconds are optional and supported. For example, Excel infers 13:20:00 as a Time value. Also, Excel infers 13:20:00.001 as Time. Excel supports fractional seconds in the grid for exporting as well.
Note Eastern Time is five hours behind Coordinated Universal Time. Excel supports everything except the UTC notation "-05:00", and "Z". The "Z" follows the decimal seconds, indicating that the specified time is UTC. Excel formats and infers the time component as date/time, but treats values containing "Z" and UTC differences as a String in a date/time cell. Excel does not incorporate the UTC difference calculation into the data.
On export, the XML Mapper reconstructs the date/time Variant value into the proper XSD format.
Excel format: YYYY-MM-DD
Excel infers the notation "1/02/2005" as a String on import. If, in the grid, you format this cell as a Date, Excel exports the displayed value. For example, if you format to mm/dd/yyyy, Excel exports 01/02/2005. If you format the cell to m/d, Excel exports 1/2.
Excel treats dates before 1900 and after 9999 in the grid as a String, but formats and infers them as date/time, per the XSD data type.
As with the Time format, Excel supports everything except the UTC notation "-05:00", and "Z". In this format, "Z" follows the decimal seconds, indicating that the specified time is Coordinated Universal Time. Values containing "Z" and Coordinated Universal Time differences are treated as a String.
Excel format: M
As displayed in the example, the value that is handed to the grid is 5/1/1900.
Export: Value exported is the month portion of what is in the grid, surrounded by two dashes.
Excel format: YYYY-MM
The value handed to the grid is 2/1/1999.
Export: Value exported is year month portion of date/time variant, separated by a dash.
Excel format: D
The value handed to the grid is 1/31/1900.
Export: Value exported is day portion of what's in the grid, preceded by three dashes.
Excel format: MM-DD
The value handed to the grid is 5/31/1900.
Export: Value exported is the month day portion of what's in the grid, preceded by two dashes, separated by a single dash.
Note For additional information on XSD data type support, see Excel Help.
There are some XML schema constructs that Excel does not support. The following list details the XML schema constructs that you cannot import into Excel:
<any>
<anyAttribute>
<substitutionGroup>
The following rules are used by Excel for processing XSDs:
minOccurs
<element maxOccurs="unbounded">
minOccurs/maxOccurs
<sequence>
Note The <sequence> compositor aggregates other elements and compositors, and in the instance document, all of the elements/compositors must appear in the prescribed order, subject to the minOccurs/maxOccurs optional properties defined for them.
<Choice>
Note A <choice> compositor aggregates elements and compositors, and in the instance document, any one (and only one) of the elements/compositors may appear.
<choice>
<all>
Note The <all> compositor, like all other compositors, groups together items that must occur in an instance of the complex type to which it belongs. Unlike <sequence> compositor, the grouped items may occur in any order in an instance document, not just in the order they are listed under the compositor.
maxOccurs="1"
<sequence maxOccurs="unbounded">
maxOccurs="1".
maxOccurs
If the elements wrapped by the <sequence> compositor occur more than one time and at least one element does not occur consecutively in the instance document in their immediate context, then the sequence is unbounded, and each element's maxOccurs="1". For example, they are A,B,C,A,B,C or some other random order other than A,A,A,B,B,B,C,C,C.
In general, XML instances that contain elements from more than one namespace have as many different XSD schema files as there are namespaces referred to in the XML. Excel generates multiple XSD files on export, one for each namespace. The XML that Excel exports may be invalid because of the action of deriving the schema. If you want a better experience, provide Excel with the XSD files so it does not need to infer the schema.
Excel infers a schema when importing or exporting XML data in the absence of a schema. The structure of the inferred schema depends on the XML data you are importing or exporting. Understanding how the structure of your data affects the resulting schema can help you understand how to modify the structure to get the schema you need.
For more information on schemas and XML in Excel, see the following articles:
Using Schemas with Word 2003 and Excel 2003
Importing XML Maps, XML Lists, and Dynamic Chart Sources in Excel 2003
Using the Excel 2003 Object Model to Add XML Data Integration | http://msdn.microsoft.com/en-us/library/aa203732%28office.11%29.aspx | crawl-002 | refinedweb | 1,202 | 53.51 |
#include <stdlib.h> int rand(void);
void srand(unsigned int seed);
int rand_r(unsigned int *seed);
The rand() function uses a multiplicative congruential random-number generator with period 232 that returns successive pseudo-random numbers in the range of 0 to RAND_MAX (defined in <stdlib.h>).
The srand() function uses the argument seed as a seed for a new sequence of pseudo-random numbers to be returned by subsequent calls to rand(). If srand() is then called with the same seed value, the sequence of pseudo-random numbers will be repeated. If rand() is called before any calls to srand() have been made, the same sequence will be generated as when srand() is first called with a seed value of 1.
The rand_r() function has the same functionality as rand() except that a pointer to a seed seed must be supplied by the caller. If rand_r() is called with the same initial value for the object pointed to by seed and that object is not modified between successive calls to rand_r(), the same sequence as that produced by calls to rand() will be generated.
The rand() and srand() functions provide per-process pseudo-random streams shared by all threads. The same effect can be achieved if all threads call rand_r() with a pointer to the same seed object. The rand_r() function allows a thread to generate a private pseudo-random stream by having the seed object be private to the thread.) | http://docs.oracle.com/cd/E36784_01/html/E36874/rand-r-3c.html | CC-MAIN-2017-43 | refinedweb | 241 | 62.61 |
From: williamkempf_at_[hidden]
Date: 2001-06-27 13:17:22
--- In boost_at_y..., Beman Dawes <bdawes_at_a...> wrote:
> At 01:08 PM 6/27/2001, Greg Colvin wrote:
> >For the reasons Peter and I have laid out I still prefer:
> >
> > namespace thread {
> >
> > struct ref {
> >
> > // ref is copyable, and all copies compare ==
> > ref(const ref& other);
> > ref& operator=(const ref& other);
> > bool operator==(const ref& other) const;
> > bool operator!=(const ref& other) const;
> >
> > // To allow us to not need current(), at least for
> > // comparison. Not needed if we have current().
> > bool is_current() const;
> >
> > bool is_alive() const;
> >
> > // Waits for the thread to finish
> > void join();
> > };
> >
> > // maybe don't need this if we have ref::is_current()
> > ref current() const;
> >
> > ref create(detail::threadproc proc); // Starts the thread
> >
> > void sleep(const xtime& xt);
> > void yield();
> > };
I'll speak for him and he can correct me if wrong ;).
> What about detach()?
Not needed. The detach() method serves no purpose when the
underlying thread information is ref-counted. This state information
is simply destroyed when there are no more references (including an
internal one maintained by the running thread). The pthread library
requires a detach() to clean up thread data properly since it does
not (explicitly) use ref-counting for this state information.
That said, detach() may still be a requirement, unfortunately. I'm
not sure what pthreads defines the behavior as if the main thread
terminates and there are other threads that have not yet been
detached still running. In fact, this issue *may* complicate the
whole concept of ref-counting, though I suspect it's a non-issue.
> What about ~ref()?
Probably just forgotten. It's a necessity to manage the ref-count.
> Was the omission of these deliberate? (Just curious:-)
One probably was, the other probably wasn't ;).
Bill Kempf
Boost list run by bdawes at acm.org, gregod at cs.rpi.edu, cpdaniel at pacbell.net, john at johnmaddock.co.uk | https://lists.boost.org/Archives/boost/2001/06/13772.php | CC-MAIN-2019-47 | refinedweb | 317 | 66.84 |
THIS PUBLICATION IS NOT TO BE SOLD. It is a free educational service in the public interest, published by the United Church of God, an International Association.
You Can Understand Bible Prophecy
© 1999,Church 2008 United Church of God, an International Association © 2007 United of God, an International Association All rights reserved. All rights reserved. Printed Scriptures in this publication quoted from the (© Printed in U.S.A. Scriptures in in thisU.S.A. booklet are quoted from the Neware King James Version New King James Version (© Nelson, 1988 Thomas Nelson, Inc., publishers) unless otherwise noted. 1988 Thomas Inc., publishers) unless otherwise noted.
2
Why Prophecy?
You Can Understand Bible Prophecy
Why Prophecy?
Contents
W
e.
3 Why Prophecy? Prophecy is an integral part of the Bible, God’s inspired revelation to mankind. Through it God reveals Himself, His plan for humanity and why we are here.
8 The Fundamentals of Bible Prophecy Bible prophecy is built around a framework of specific principles and themes. Knowing them is key to unlocking a proper understanding of Bible prophecy.
19 Promises and Covenants: A Prophetic Legacy
No confidence
Many crucial Bible prophecies begin with one individual and his descendants. What promises will God fulfill through the family of Abraham?
28 God Confirms His Credibility to the World Can we believe Bible prophecy? Through the examples of the kingdoms of Israel and Judah, God gave unmistakable proof that His prophecies are sure.
37 The International Scope of Prophecy Though much of prophecy is focused on specific peoples, God’s plan extends to all nations. He reveals how He will ultimately deal with all of humankind.
42 The End of “This Present Evil Age” Many Bible prophecies deal with the time that appears to lie immediately before us—the end of the age of the rule of Satan the devil over the world.
Wars and acts of terrorism threaten to endanger the fabric of society and make even more elusive the security we seek. Uncertainty is a way of life.
63 The Millennial Reign of Jesus Christ
What happens after the Millennium, Jesus Christ’s 1,000-year reign over mankind? This is when a truly astounding part of God’s great plan comes to pass!
U.S. Air Force
Beyond the tumultuous times of today lies the promise of a transformed world of peace and plenty—the age of Christ’s glorious reign on the earth!
70 Beyond the Millennium
3
4
Why Prophecy?
You Can Understand Bible Prophecy Holy Bible. The Bible is unique among all literature. Though foretold!
iStockphoto
Why is our world so uncertain? Is nothing predictable? Must we live in ignorance of our future? Can we discover a source for information about where this world is headed? penned by many writers from varied cultures over a span of 15 centuries, it is the masterpiece of a single author, the Creator of the universe. For centuries Bible students have marveled that so many writers, from strikingly dissimilar backgrounds, could maintain the consistent message and purpose
5
6
Why Prophecy?
You Can Understand Bible Prophecy
mission of the Messiah, Jesus of Nazareth, are depicted as examples of His devotion to the welfare of people. Many prophecies yet to be fulfilled are directly related to the future work and mission of Jesus Christ.
Adam, explains the reason for our nature. It tells us how and why sin, evil and suffering entered the world and reveals God’s solution to that problem. It reveals the purpose of our existence, explaining why God made human beings and the incredible future He has in store for: the foundation of prophecy
Precise details about Jesus’ birth, ministry and crucifixion were accurately foretold hundreds, even thousands, of years before He was born. with Him as His children—that our salvation will always be His greatest concern. Read on time began” (2 Timothy 1:9)—and why His continuing efforts are crucial to the success of God’s plan and purpose for our future. Come with us on a journey to explore and understand Bible prophecy. Designpics
7
8
The Fundamentals of Bible Prophecy
You Can Understand Bible Prophecy
The Fundamentals of Bible Prophecy
point directly or indirectly to the mission and work of Jesus the Messiah. 2. The Kingdom of God: focus of prophecy
The prophetic focus of Jesus Christ’s mission is the Kingdom of God. During His earthly ministry “Jesus traveled
W
hy did God inspire the writers of Scripture to see how they fit together like pieces of a puzzle.
1. The role of the Messiah
Prophecy discloses many details of God’s great design. It explains God’s actions in human affairs and how they relate to His revealed plan.
Shaun Venish. It is only natural for us to wonder about the prophecies that concern His second appearing—advance news languages, respectively. Both mean “Anointed One,” one who is divinely chosen.) Though not specifically mentioned in every prophetic passage, the Messiah is the central figure of prophecy. In fact, a major purpose of prophecy is to reveal the mission). Without knowledge of Christ’s role in these prophecies, His disciples could not understand them. Most prophecies pertaining to the future
9
to the setting up of His rule and authority over humanity: ).
10
The Fundamentals of Bible Prophecy
You Can Understand Bible Prophecy to God: .
Bible prophecy often reveals specific events and sequences of events. But rarely does it reveal the exact time when events will occur. of hope is a dominant theme in the writings of the prophets of God.
4. Specific dates are rare
Designpics honor me with their lips, but their hearts are far from me” (Isaiah 29:13, NIV). God describes people as having “heart[s] of stone”—an unyielding attitude toward Him and His instruction. This hardheartedness leads us to lives of selfishness—of greed, envy and hatred—which bring us ever closer to the brink of destruction. Bible prophecy, however, reveals how God will ultimately deal with
11. It is not God’s purpose that we know the exact time of the fulfillment of most prophecies. He wants us to recognize the many prophecies that have already been fulfilled. Their fulfillment assures us that God’s promises are accurate and reliable. Christ’s disciples asked on another occasion, “When will these things be?” (Matthew 24:3). Jesus listed several trends that have continued from His day down to our own—religious deception, wars, famines,
12
You Can Understand Bible Prophecy
Jesus Christ’s Life and Death in Prophecy
M
any. (Isaiah 11:1-5;40).). Jesus Himself could not have controlled how.
The Fundamentals of Bible Prophecy
13
uncontrollable disease epidemics and devastating earthquakes and storms. “All these things must come to pass,” He advised, “but the end is not yet” (verse 6). He did not give them a specific sign that would herald His coming. Rather, He stressed the need to “take heed”—to be spiritually alert and on guard—that they should not be deceived (verse 4). Only the Father knows the precise time of His Son’s return. Yet we can understand important prophecies and prophetic principles that give clear indication His return is imminent. For example, the prophet Daniel asked an angel to explain certain end-time prophecies that had been revealed to him. “Go your way, Daniel,” the angel responded, “for the words are closed up and sealed till the time of the end” (Daniel 12:6-9). This scripture and others indicate that the time of the end will be discernable to God’s people, though likely not until that time begins. A number of specific prophecies will be fulfilled in the period leading up to and including unparalleled world trouble lasting 31⁄2 years (in biblical language, “a time [a year], times [two years, the smallest plural being implied by the lack of specificity] and half a time [half a year],” verse 7), which will conclude with the establishment of God’s Kingdom on earth. 5. Duality in Bible prophecy).
14
The Fundamentals of Bible Prophecy
You Can Understand Bible Prophecy. In the Olivet prophecy, Jesus spoke of an “abomination of desolation.” Daniel’s prophecy about the abomination of deso lation was fulfilled in 167 B.C. by Antiochus Epiphanes, but Jesus pointed out that the prophecy would have a future fulfillment (see “The Coming ‘Abomination of Desolation’ beginning on page 54).. We should also understand that virtually all interpretations of how prophecies may be fulfilled are speculative to some degree, and often we may recognize a prophecy’s fulfillment only after it is well underway or already has taken place. command-
Leviticus 26 and Deuteronomy 28 illustrate God’s blessings for obedience and punishment for disobedience.
Photos: iStockphoto,
15
ments … [lest] when your heart is lifted up … you say in your heart, ‘My.
16
You Can Understand Bible Prophecy.
The Fundamentals of Bible Prophecy
17
Prophecy out of context is easy to misinterpret. This is why irrational interpretations of prophecy have abounded throughout the centuries. 8. This is Satan’s age, not God’s). As Paul explained, Christians must in this age struggle “against all the various Powers of Evil that hold sway in the Darkness around us, against the Spirits of Wickedness on high” (Ephesians 6:12, Twentieth Century New Testament). position chose to become an adversary to God and was therefore renamed Satan, which in Hebrew means “adversary.” Revelation 12:4 indicates that Satan (called a dragon here and in verse 9) drew a third of the angels into rebellion. The angels who follow him are demons, the evil forces Paul warns us about.. “So God created man in His own image; in the image of God He created him; male and female He created them.
18
You Can Understand Bible Prophecy). Eventually God will greatly extend that rule, as the book of Hebrews explains in expounding on Psalm 8: “‘What download.
Promises and Covenants: A Prophetic Legacy
19
Promises and Covenants: A Prophetic Legacy
P
rophe, ‘And to seeds,’ as of many, but as of one, ‘
20
Promises and Covenants: A Prophetic Legacy
You Can Understand Bible Prophecy.
God changed Jacob’s name to Israel (Genesis 32:28).
Dual promises
God told Abraham, “Get out of your country, from your family and from your father’s house, to a land that I will show you. I will make you a great nation; I will bless you and make your name great.”. Woodcut by Gustave Doré [‘exalted father’], but your name shall be Abraham [‘father, a forerunner, of things to come (Romans 9:6-9). Isaac fathered two sons, Esau and Jacob. God chose Jacob, the younger one, to receive the physical promises He gave to Abraham. God similarly chooses those to whom He offers the opportunity to be among the spiritual descendants of Abraham and receive the fulfillment of the eternal, spiritual promises (Romans 9:10-11). God places conditions, of course. All must first come to understand His revealed truth, then repent of their sins (1 Timothy 2:3-4; 2 Peter 3:9).
21
22
You Can Understand Bible Prophecy were broken off [referring to Israelites being cut off for disobedience],,” he writes,
Promises and Covenants: A Prophetic Legacy
23
were hardened, as it is written, ‘God gave them a sluggish spirit, eyes that would not see and ears that would not hear, down to this very day’” (verses 7-8, NRSV). “So I ask, have they stumbled so as to fall? By no means! But through their stumbling [over Christ, their ‘stone!” (Romans 11). Shortly before Jacob’s death, God inspired him to reveal to his 12 sons the manner in which the physical heritage of Abraham would affect the generations of Israel. “And Jacob called his sons and said, ‘Gather to only Joseph and Judah. To each came a different promise, a separate heritage. The Bible summarizes: “Though Judah became prominent among his brothers and a ruler came from him, yet the birthright belonged to Joseph” (1 Chronicles 5:2, NRSV).
24
Promises and Covenants: A Prophetic Legacy
You Can Understand Bible Prophecy.
Because of that birthright promise, Joseph’s descendants would enjoy inconceivable prosperity—possessing the finest material blessings—and achieve great military superiority because the hand of God would be with them. They would increase greatly, colonizing beyond their borders).
David’s kingdom divided
Promises to David
Long after Abraham, through King David of the tribe of Judah, the scepter promise finally took on even greater signi ficance. God gave David the kingdom of Israel and promised that from him would spring a dynasty of kings that would continue forever.
Illustration by Michael Woodruff
God chose David to be king over Israel. He also promised that from him would come). God did indeed establish a dynasty of kings through David. God promised that a greater future King would come from David’s descendants. He sent an angel to Mary who told her: “You will conceive in
25 nation. The birthright and scepter promises then followed separate paths until the kingdom of Judah was toppled by the Babylonians and the Jewish throne was transferred to Israel in a distant land. And ultimately the house of Israel and the house of Judah will one day be reunited as one nation under the rule of the Messiah. (To better understand these promises and the vital role they play in the fulfillment of Bible prophecy, be sure to download or request your free copy of our booklet The United States and Britain in Bible Prophecy and read our online publication The Throne of Britain: Its Biblical Origin and Future.) A reunited kingdom
The restoration of Israel as one nation under the rule of Christ is a
26
You Can Understand Bible Prophecy: ‘To). This agreement was in essence a marriage covenant between God and the people (Jeremiah 3:20; 31:32). The purpose of covenants
Every biblical prophet from the time of Moses forward used this covenant as the standard for evaluating and judging the behavior of God’s
Promises and Covenants: A Prophetic Legacy
27 now.
28
God Confirms His Credibility to the World
You Can Understand Bible Prophecy
29
God Confirms His Credibility to the World
in their own words and style, what they saw or heard (verse 8). Sometimes God told them what to say. Many prophetic passages are introduced with the words, “Thus says the Lord …” (Isaiah 44:6; Jeremiah 8:4; Ezekiel 11:5).
hat is a prophet? What is he sent to do? Peter describes prophets as “holy men of God [who] spoke as they were moved by the Holy Spirit” (2 Peter 1:21). But is that the whole story? “The Hebrew word for prophet, nabi, means ‘one who announces or brings a message from God.’ Our word ‘prophet’), ‘for’ and ‘before’;.
W
Israel’s spiritual decline
Photos: Scott Ashley
God repeatedly warned Israel and Judah of national punishments if they continued to rebel against Him. As God had prophesied, both kingdoms were taken into captivity..
30
God Confirms His Credibility to the World
You Can Understand Bible Prophecy keeps His promises
God repeatedly warned the Israelites that He would punish them through the Assyrians, led by King Sargon (left) and his successors. Eventually they were taken captive. in the early chapters of 2 Kings. Ultimately the prophets began to proclaim their prophetic warnings not only with spoken appeals but with written prophetic messages.
Photos: Scott Ashley
Written prophecy became necessary
31
32
You Can Understand Bible Prophecy
God Confirms His Credibility to the World
33
History Proves Bible Prophecy’s Accuracy
C” (2 Kings 17: “The Lord has sent to you all His servants the prophets, rising early and sending them, but you have not listened nor inclined your ear to hear. They.’ “‘Yet you have not listened to Me … Because God fulfills His promise destroyed by Nebuchadnezzar were also fulfilled The 70 years in exile passed. Daniel 5 records down to the last detail. The books of Ezra and that the Babylonian monarch Belshazzar held Nehemiah record the Jews’ return from exile. a great and blasphemous feast at which he and his guests drank wine from gold and silver Fulfilled prophecy’s meaning for us A series of remarkable prophecies spanning vessels looted from the Jerusalem temple years before by Nebuchadnezzar. The king watched as hundreds of years, five kingdoms and many a ghostly hand appeared and wrote a mysterious prophets and rulers precisely came to pass. As message on the wall. The king “was so fright- God had said through Isaiah when He foretold ened that his knees knocked together and his Judah’s downfall at the hands of the Babylonians: “I am God, and there is no other; I am legs gave way” (verse 6, NIV). The prophet Daniel revealed that this original God, and there is none like Me, declaring the handwriting on the wall signified God’s judgment end from the beginning, and from ancient times that Babylon’s dominance had come to an end. things that are not yet done, saying, ‘My counsel He told the king, “‘Your kingdom is divided and shall stand, and I will do all My pleasure’… Indeed given to the Medes and Persians’… [and] that I have spoken it; I will also bring it to pass. I have very night Belshazzar, king of the Babylonians, purposed it; I will also do it” (Isaiah 46:9-11). God alone has the power to prophesy events was slain” (verses 28, 30, NIV). A century later the Greek historian Herodotus and then bring them to pass. He will yet bring (484-420) confirmed Daniel’s account of the to pass the many other unfulfilled prophecies fall of Babylon: “The Persians, drawing off the recorded in His Word. For additional proof that the Bible is indeed river [Euphrates] by a canal into the lake, which was till now a marsh, he [Cyrus] made the God’s inspired Word, be sure to download or stream to sink till its former channel could be request your free copy of Is the Bible True?
34
You Can Understand Bible Prophecy will demonstrate that He is God
Through the prophet Ezekiel, God explains the great purpose for the events He has revealed to us: “‘I: ‘Now I will bring back the captives
God Confirms His Credibility to the World
35). God will confirm His credibility. “‘And a Redeemer will come to Zion [Jerusalem], and to those who turn from transgression in Jacob,’ declares the Lord. ‘And as for Me, this is My covenant with them,’ says the Lord: ‘My Spirit which is upon you, and My words
36
You Can Understand Bible Prophecy
which I have put in your mouth, shall not depart from your mouth, nor from the mouth of your offspring, nor from the mouth of your offspring’s offspring,’ says the Lord, ‘from.
The International Scope of Prophecy
37
The International Scope of Prophecy
S
kept nations.
38
The International Scope of Prophecy
You Can Understand Bible Prophecy.
chadnezzar, the gentile king of Babylon, an unusual opportunity to serve Him. Daniel, the prophet who was a key administrator in Nebuchadnezzar’s government, recorded that God offered this gentile monarch the chance,
God loved the world
Through a dream, God revealed to Babylon’s King Nebuchadnezzar that a series of kingdoms would arise. The image the king saw was composed of four types of metal, which corresponded to the four great empires.
Illustration by Pablo Loayza Nebu-
39
40
The International Scope of Prophecy
You Can Understand Bible Prophecy was through Daniel: .
A lesson of history
What God has shown, and history has repeatedly demonstrated, is that neither national leaders nor their people are able consistently to obey
Photo illustration by Shaun Venish/PhotoDisc
Prophecy shows how the Creator God will intervene in mankind’s affairs and establish His Kingdom, which will bring peace, righteousness and salvation to all humanity. have no indication that he permanently changed his idolatrous ways and began serving only the true God. He came to understand, however, that Daniel’s God was greater than all the other gods he worshipped.
41
42
The End of “This Present Evil Age”
You Can Understand Bible Prophecy
The End of ‘This Present Evil Age’.
N
ow as [Jesus] sat on the Mount of Olives, the disciples came to Him privately, saying, ‘Tell us, when will these things be? And what will be the sign of Your coming, and of the end of the age?’” (Matthew 24:3). They wanted to know when the age of human misrule under, REB).?
It’s difficult to imagine the magnitude of suffering that will take place during a few terrifying years at the end of our age. Mercifully, that frightening time will quickly pass.18; 17:12-13).
The unseen hand of the archdeceiver
As we’ve seen, the Bible warns us of Satan the devil’s deception of mankind. Through this deception he has made himself the ruler and god of this present age. Just before Jesus returns, God Almighty will permit Satan to finally mank ind to make use of the extended family as the foundation for organization and structure. Nimrod, however, persuaded the people of his time to reject God’s plan in
The symbolic beast will rise again
Corbis Digital Stock
‘‘
43
Chapter 12 of Revelation pictures Satan as “a great, fiery red dragon having seven heads and ten horns, and seven diadems on his heads” (verse 3). It describes his attempt to destroy Jesus Christ shortly after His birth: “And the dragon stood before the woman who was ready to give birth, to devour her Child as soon as it was born” (verse 4; compare Matthew 2:13-21). At length the scene shifts to the time of the end: “Therefore rejoice,
The End of “This Present Evil Age”
You Can Understand Bible Prophecy, ‘Who is like the beast? Who is able to make war with him?’” (verse 4). The world
45
will fear and marvel at the enormous power of this alliance of nations. Notice the configuration of this political and military alliance. ).12). This beast claims
The time of the end of Satan’s reign on earth will be marked by human suffering and man-made and natural catastrophes unparalleled in history.
Photos: iStockphoto
44
to represent Jesus Christ—the true Lamb of God (verse 8)—but actually speaks for Satan concerning what people are to worship. In Revelation 17 this beast is also pictured
46
You Can Understand Bible Prophecy: .’” Satan’s political and religious systems are rooted in the popular conviction that man has the right to decide for himself what is right and wrong. Illusion of peace
The devil boasted to Jesus Christ of his power and control over “all the
The End of “This Present Evil Age”
47lived.
48
You Can Understand Bible Prophecy vicin-
Bible prophecy indicates that, as the age of man draws to a close, political and military leaders will unleash violence and destruction on an unimaginable scale. Hundreds of millions will lose their lives. ity of Jerusalem for the most terrifying military showdown in history. Jerusalem is considered a holy city by three of this world’s great religions. Geographically, it is in one of the most strategically important locations on earth—the crossroads of the continents of Africa, Asia and Europe. The battle of the great day of God Almighty
To assemble these armies, Satan will send “spirits of demons, performing signs … to the kings of the earth and of the whole world, to gather
The End of “This Present Evil Age”
49 just wrath of God (Revelation 14:9-10). A large faction in this final battle—the beast power supported by a coalition of 10 rulers—will amass its armies on the plain near the ancient military stronghold of Megiddo in northern Israel: “And they gathered them together to the place called in Hebrew, Armageddon” (Revelation 16:16). The very word Armageddon (the Greek form of the Hebrew Har Megiddo was told, outlandish to take seriously. But it is real. It will happen. The apostle Paul spoke plainly of this earth-shaking time: “For you yourselves know perfectly that the day of the Lord so comes as a thief in the night [at an unexpected time]. For when they say, ‘Peace and safety!’ then sudden destruction comes upon them, as labor pains upon a pregnant woman. And they shall not escape” (1 Thessalonians 5:2-3). When the world’s final effort for international unity to ensure in the cataclysmic events of what the Bible calls “the great and awesome day of the Lord”? (Joel 2:31). God’s ultimate goal has always been to bring all people to repentance (2 Peter 3:9). But a repentant humanity is impossible as long as most people follow Satan’s lead in proudly exalting human opinions and
50
You Can Understand Bible Prophecy. Through the prophet Zephaniah, God explained that He, ‘You: “‘The Redeemer will come to Zion,.
The End of “This Present Evil Age”
51
Why are such drastic measures necessary? Notice Paul’s description of humanity’s prevailing attitude at the time of the). Mankind’s attitude and motivation must change. The haughty, headstrong, unloving and brutal attitudes dominating the world
The survivors from this brief but devastating period will be primarily people whose hearts have softened and who have been humbled by their experiences.
52
You Can Understand Bible Prophecy would occur. The prophet Zephaniah described that day of reckoning for mankind’s collective evil and rebellion: “The great day of the Lord is … a day of wrath, a day of trouble and distress, a day of devastation and desolation … ‘Ianiah 31⁄2 gentile control. Jerusalem’s fall back then directly relates to events at the end of the age. In 586 there at His return (Luke 1:32-33).
The End of “This Present Evil Age”
53, setting up an “abomination” in this designated holy place (Daniel 11:31; 12:9-11)—a defilement that included an idolatrous image in the earlier, prototypical fulfillment of this prophecy (see “The Coming ‘Abomination of Desolation’” beginning on page 54). This scenario seems to be the most likely way these prophecies could be fulfilled in light of current conditions. Notice the terrible significance Jesus places on this
54
You Can Understand Bible Prophecy
The End of “This Present Evil Age”
55
The Coming “Abomination of Desolation”
I).
The temple defiled.
Later prophetic fulfillment.
Lessons from the first fulfillment.
56
You Can Understand Bible Prophecy
flight will not take place in winter or on the Sabbath. For then there will be great distress, unequaled from the beginning of the world until now—and never to be equaled. “‘And I will give power to my two witnesses, and they will prophesy one thousand two hundred and sixty days [31⁄2 [like Moses in Egypt],). Set against each other for 42 months, or 31⁄2 years, will be these opposing pairs of spiritual leaders—one pair representing God, the other pair representing Satan and his system. The beast of Revelation
It:
The End of “This Present Evil Age”
57
in blasphemy against God, to blaspheme His name, His tabernacle, and those who dwell in heaven. It was granted to him to make war with the saints and to overcome them” (Revelation 13 and martyrdom birth pains” (Matthew 24:8, NIV). These precede the time of God’s wrath, the Day of the Lord. Once these conditions and
58
The End of “This Present Evil Age”
You Can Understand Bible Prophecy
events begin, they continue to the very end of the age—increasing in frequency and severity like labor contractions. The intensity of destruction rapidly escalates from their cumulative effects as the end approaches. The first six seals in Revelation 6 summarize major events and conditions that lead up
Photo illustrations: iStockphoto
Jesus Christ warned that unless the terrifying events of the time of the end were cut short, “no living thing could survive.” Only in recent decades has it been possible for this sobering prophecy to be fulfilled.
59
of many will grow cold. But he who endures to the end shall be saved” (Matthew 24:9-13). Christ describes this frightening time as one of “great tribulation,” an era unparalleled in).
60
You Can Understand Bible Prophecy make up calamities “to the sixth angel who had the trumpet, ‘Release the four angels who are bound at the great river Euphrates.’ So
61
The End of “This Present Evil Age”
the four angels, who had been prepared for the hour and day and month and year, were released to kill a third of mankind. Now the number of the army of the horsemen was two hundred million” (Revelation 9. Shortly, His, ‘The
What Is “the Lord’s Day”?
S
ome people mistakenly assume that, when the apostle John wrote that he “was in the Spirit on the Lord’s Day” (Revelation 1:10),). Jesus Christ said He was the “Lord of the Sabbath” (Mark 2:28), not some other day of the week (compare Isaiah 58:13). However, the context of John’s vision shows that he wasn’t referring to a day of the week at all. Instead, he wrote that the vision trans-
ported)..
62
You Can Understand Bible Prophecy
angel took up a stone like a great millstone and threw it into the sea, saying, ‘Thus with violence the great city Babylon shall be thrown down, and shall not be found anymore’” (Revelation 18:21). John describes Christ’s victory at Jerusalem in the Valley of Jehoshaphat (see also Joel 3:2, 12-14) in will then begin the work of bringing genuine peace and righteousness to mankind. In the next chapter we will see God’s prophets’ description of the incredible world Jesus Christ will build as He restores the rule and ways of God.
The Millennial Reign of Jesus Christ
63
The Millennial Reign of Jesus Christ
W
hen.
64
You Can Understand Bible Prophecy. Paul explained: ).
The Millennial Reign of Jesus Christ
65: :21-22). And through Jeremiah: “Now therefore, thus says the Lord, the God of Israel, concerning this city [Jerusalem] of which you say, ‘It shall be delivered into the hand of the king of Babylon by the sword, by the famine, and by the pestilence’: ‘Behold,’” (Jeremiah 32:36-39). Since Christ will establish Jerusalem as His capital, the first people to experience the effects of His rule will be the restored kingdom of Israel. As their King, He will immediately establish a close working). … I will heal them and reveal to them the abundance of peace and truth. And I will cause the captives of Judah
66
The Millennial Reign of Jesus Christ
You Can Understand Bible Prophecy inspire other nations to seek the same way of life and to want to reap the same blessings:
Under Jesus Christ’s rule, the world will be transformed into a paradise of peace and plenty. “Everyone shall sit under his vine and under his fig tree, and no one shall make them afraid” (Micah 4:4).
The fruit of right knowledge
With Jesus Christ as King, Jerusalem will be the center of learning for the world. God’s Word, the Bible, will provide a solid foundation
PhotoDisc
in their own lands: ). Eventually “the earth shall be full of the knowledge of the Lord as the waters cover the sea” (Isaiah 11:9).
67,
68
The Millennial Reign of Jesus Christ
You Can Understand Bible Prophecy).
“‘The wolf and the lamb shall feed together, the lion shall eat straw like the ox … They shall not hurt nor destroy in all My holy mountain,’ says the Lord” (Isaiah 65:21-25).
Photo illustration by Shaun Venish/Corel Professional Photos/PhotoDisc
Physical blessings
As people the world over begin to obey God, first by getting their spiritual priorities straight, they will begin to experience unprecedented physical prosperity: “‘Behold, the days are coming,’ says the Lord, ‘when build houses and inhabit them; they shall plant vineyards and eat their fruit. They shall not build and another inhabit; they shall not plant and another eat; for like the days of a tree shall the days of my people be,
69.
70
W
You Can Understand Bible Prophecy
Beyond the Millennium
e have seen” (verse). Satan released for a short time
Also, the apostle John in Revelation describes his vision of the transition to Christ’s reign in which he saw
Beyond the Millennium
71.. The general resurrection of the dead
Now the greatest judgment of all must begin. As we read earlier, at Jesus Christ’s return whom God called during the Millennium. They will all be raised from the dead with a marvelous opportunity to know God for the first time!
Beyond the Millennium
You Can Understand Bible Prophecy. What are the criteria for this judgment? Two factors are involved. These people are judged “by the things which were written in the books” and “according to their works” (verse 12). The Greek word translated “books,” biblion, apparently refers here to, taught the truth of God even heard of Jesus Christ and the Bible.
73
People from all human eras resurrected
This period is the time for all other people to learn the truth of God and enjoy the same opportunity for salvation given to those who lived during the Millennium. are condemned to hell or purgatory at death, the Bible reveals that all will have the opportunity to choose whether they will learn God’s way, repent and receive God’s gift of eternal life. iStockphoto
72
Details of this great resurrection
What will happen when these people come back to life for this time
74
You Can Understand Bible Prophecy
of judgment? The prophet Ezekiel gives us the answer. In a vision he sees a huge valley full of dried bones, all that remained of many longdead. God’s judgment is complete restored initially to physical, fleshly existence (Ezekiel 37:4-10). They are mortal,
Beyond the Millennium
75.”
76
(verses 51-54)..
The eternal family of God
Another paradise
The biblical account of man begins in the Garden of Eden at the head of four rivers. In the midst of that garden God placed the tree of life and the
The number of people who will come to repentance and receive eternal life will be like the stars in the heavens and the sand on the seashore—beyond the natural ability of any human being to count them.
PhotoDisc Jesus Christ (Matthew 25:1), who is “the firstborn among many brethren” (Romans 8:29). God the Father Himself dwells among them: “And I heard a loud voice from heaven saying, “Behold, the city indicate the awesome success Jesus Christ will have in bringing the overwhelming majority of people who
77
Beyond the Millennium
You Can Understand Bible Prophecy
78
You Can Understand Bible Prophecy
War and Peace in the Middle East
79). All sorrow and suffering will be gone forever (Revelation 21:4). You can know the future
At the outset we posed a question: Must we remain ignorant of our future? Now we can see that)..”
much is happening in the and so quickly, that Sit’soworld, almost impossible to sort
• Also request or download free copies of these eye-opening booklets at: You Can Understand Bible Prophecy, The Book it all out. of Revelation Unveiled, The Middle Where are today’s dramatic and danger- East in Bible Prophecy, The Gospel ous trends taking us? What does Bible of the Kingdom and Are We Living prophecy reveal about our future? Is in the Time of the End? You can’t prophecy coming to pass before our afford to be without this crucial eyes? How can you know the answers?: 265 01 687 022 Contributing writers: Scott Ashley, Gary Petty Editorial reviewers: John Bald, Wilbur Berg, Jim Franks, Bruce Gore, Paul Kieffer, Graemme Marshall, Burk McNair, Mario Seiglie, Richard Thompson, David Treybig, Leon Walker, Donald Ward, Lyle Welty Cover: Photo illustration by Shaun Venish/Corbis Digital Stock/PhotoDisc/Scott Ashley UP/0806.
UP/0806/2.0
Prophecy is an integral part of the Bible, God's inspired revelation to mankind. Through it God reveals Himself, His plan for humanity and...
Published on Sep 10, 2010
Prophecy is an integral part of the Bible, God's inspired revelation to mankind. Through it God reveals Himself, His plan for humanity and... | https://issuu.com/united-church-of-god/docs/you-can-understand-bible-prophecy?e=2041973/2819445 | CC-MAIN-2020-34 | refinedweb | 6,096 | 68.91 |
Created on 2012-04-23 22:53 by Albert.Zeyer, last changed 2012-04-24 15:10 by python-dev. This issue is now closed.
```
class Foo1(dict):
def __getattr__(self, key): return self[key]
def __setattr__(self, key, value): self[key] = value
class Foo2(dict):
__getattr__ = dict.__getitem__
__setattr__ = dict.__setitem__
o1 = Foo1()
o1.x = 42
print(o1, o1.x)
o2 = Foo2()
o2.x = 42
print(o2, o2.x)
```
With CPython 2.5, 2.6 (similarly in 3.2), I get:
({'x': 42}, 42)
({}, 42)
With PyPy 1.5.0, I get the expected output::
({'x': 42}, 42)
({'x': 42}, 42)
I asked this also on SO:
From the answers, I am not exactly sure wether this is considered as a bug in CPython or not. Anyway, I just wanted to post this here.
It's a CPython bug.
New changeset 971865f12377 by Benjamin Peterson in branch '3.2':
don't use a slot wrapper from a different special method (closes #14658)
New changeset 0c1c8f8955d8 by Benjamin Peterson in branch 'default':
merge 3.2 (#14658)
New changeset e3eda2d91e93 by Benjamin Peterson in branch '2.7':
don't use a slot wrapper from a different special method (closes #14658) | http://bugs.python.org/issue14658 | CC-MAIN-2016-36 | refinedweb | 199 | 79.56 |
ipyclam: Embedded IPython console in NetworkEditor
Take a look at the screenshot.
Yes, it is what it seems to be: A Qt-based IPython console embedded into CLAM NetworkEditor. Yes, ipyclam and NetworkEditor share the same network. And yes, sadly, although ipyclam sees anything we do in NetworkEditor. NetworkEditor does not refresh on ipyclam changes yet.
Still it is quite a big step forward because we have been blocked at that point for a while and it has been unblocked in just an afternoon.
In the past months, Xavi and me spent many hours looking for a proper API in IPython to do what we wanted without getting too low level (and postal). Now that IPython provided that new API (and documented examples), it has been quite straight forward to integrate.
A text console but it is not
The new Qt based IPython console is amazing. It is even better in many ways than the standard IPython terminal most of us are used to. It provides:
- syntax highlighting as you write,
- graceful multi-line edition,
- function API hints when writing calls,
- navigable tab completion,
- customizable graphical representations of results,
- many hooks to add our bells and whistles.
So it seems a text console, but it is not. Yep, we can add many bells and whistles there.
Back to the original ipyclam goal
Lately, we clearly realized that ipyclam strength is clearly empowering CLAM.
I’ll try to abstract the problem so that it could be useful beyond CLAM.
We had a domain object implemented in C++ and we wanted to provide
a Python console (a Qt widget) to manipulate it.
So the first goal, which Xavi achieved very succesfully,
is to build a Python wrapper,
ipyclam to the domain object, a
CLAM::Network.
IPython separated quite well the concepts of Python kernel from the Qt Console. Indeed it separated those concepts that much that they were at different processes and that made our goal unfeasible, at least, by using the stable high level API of IPython.
Luckily, IPython 1.3 provides high level interfaces and
examples
for having both kernel and console in the same process
connected via a local pipe.
I took that code and changed it to be able to inject the CLAM::Network
and I got a Python script that serves as Qt based
ipyclam_console
which I named
ipyclam_qtconsole.py and it is working at the repository. I modified the code from Jarosz Pawel to get the kernel encapsulated inside the console widget itself and I added a function to easily injecting
objects into the interpret main namespace, for example the ipyclam network object.
Still the example was a Python program using a PySide base widget. Gladly, we already had taken our quest to get the PySide and PyQt4 working all together with C++, and we already have a few functions to transfer up and down QObjects from and to C++. So if I can abstract the whole thing into a QWidget I could use it as is and I still can’t believe it worked that well.
namespace py = boost::python; QWidget * GetIPyClamConsole(CLAM::Network & network) { try { Py_Initialize(); // Dummy __main__ namespace, to run execs py::object _main = py::import("__main__"); py::object _main_ns = _main.attr("__dict__"); // Adding working dir to the Python search path py::exec("import sys; sys.path.append('.')" , _main_ns, _main_ns); // Simulate that we have a working command line (expected by IPython) py::exec("sys.argv=['ipyclam']\n", _main_ns, _main_ns); // Build an ipyclam network having the CLAM network as backend py::object ipyclamModule = py::import("ipyclam"); py::object proxy = py::object(py::ptr(&network)); // The proxy backend py::object net = ipyclamModule.attr("Network")(proxy); // The ipyclam network // Creating the IPython based console widget py::object consoleModule = py::import("ipyclam.ipyclam_qtconsole"); py::object console = consoleModule.attr("IPythonConsoleQtWidget")(); // Injecting the network into the namespace console.attr("namespace_inject")("net", net); // Unwrapping the PySide based qt console to use it as a abstract QWidget QWidget * consoleWidget = (QWidget*) shibokenUnwrap(console.ptr()); return consoleWidget; } catch (py::error_already_set & e) { std::cerr << "Run time Python error!" << std::endl; PyErr_Print(); return 0; } }
TODO’s
Well, still fully not working, what else we have to get done:
- Clean-up dependencies
- NetworkEditor depends on ipyclam on run-time
- NetworkEditor depends on Boost-Python and Shiboken on compile-time, has to be both?
- Refresh the canvas when Python changes the network, including:
- Processing creation and deletion
- Processing connection
- Configuration affecting connector
- Renames
- Changes on the back-end
- Providing documentation so that the Qt console hints help the user
- Polishing ipyclam for some nasty things you get when you play a little with it.
- Controling the banner and the prompt (we could control it on Terminal based but the same interface seems to be gone in Qt) | http://canvoki.net/coder/blog/2013-01-21-embedded-ipython-console.html | CC-MAIN-2018-34 | refinedweb | 790 | 52.49 |
Shankara Sharma wrote:One of the restrictions that a static method has is It can only call other static methods and it can't call a non static method from it.
But When i create an object inside a static method, i can call a non static method. Here is the code below:
public class ClassB{
public void display(){
System.out.println(" Non Static method");
}
public static void display1(){
System.out.println(" Static Method");
ClassB classB=new ClassB();
classB.display();
}
public static void main(String[] args){
display1();
}
}
Can anyone please give an explanation?
[Edit - added code tags - see UseCodeTags for details]
Shankara Sharma wrote:
We can even call a static method from non static method directly as static members part of the class.
Does static variables are loaded into memory even before an instance of that class is created?
Does memory is created for static methods and instance methods?
Shankara Sharma wrote:Creation of memory for static and non static methods in the sense, whether the memory is allocated before or after the instance creation?
Shankara Sharma wrote:So for local variables inside methods when will memory be allocated?
Dattatraya Tembare wrote:Yes, it's all about allocation of memory either in Heap or Stack.
And when we call a non-static method it’s part of Stack
Now see there are two separate memory locations which are not linked together so we can’t access static variables/methods from non-static methods.
Jeff Verdegan wrote:
Dattatraya Tembare wrote:Yes, it's all about allocation of memory either in Heap or Stack.
No, the reason for not being able to access non-static variables in a static context has nothing to do with heap vs. stack.
And when we call a non-static method it’s part of Stack
The method's variables go on the stack. The executable code for method body itself, like all methods, is on the heap, as part of the class definition.
Now see there are two separate memory locations which are not linked together so we can’t access static variables/methods from non-static methods.
No, that's not right.
The reason we can't refer to non-static members in a static context has nothing to do with where variables are stored. There is no such concept of one area of memory not being able to see the other.
It's much simpler than that. Non-static members require a "this" reference to a "current" object. There is no "this" and no "current object" in a static context. That's simply a natural consequence of what "static" means in the language and it has nothing whatsoever to do with memory layout.
Dattatraya Tembare wrote:
Please explain me what is this here... this is object of existing class & it's on heap & static context is also on heap. So it's having access. When we call methos it creates copy on stack, we are having reference of object (this) so we are able to access the static data which is on Heap.
I think creating an object is all about allocation of memory, how can you separate this? | http://www.coderanch.com/t/567249/java/java/Static-methods | CC-MAIN-2014-52 | refinedweb | 525 | 63.39 |
This example is a continuation of Planetary Motion, which discussed different constant step size ordinary differential equation (ODE) solvers (such as Forward Euler, Explicit Trapezoid, Midpoint Rule and fourth order Runge-Kutta) applied on a two dimensional one body problem. In this example we will use an adaptive step size ODE solver (Embedded Runge-Kutta pair) to solve two and three body problems. A brief motivation for the adaptive step size is explained in Adaptive Runge-Kutta Methods.
First we import the necessary libraries and set some common figure parameters.
# Import libraries import numpy as np import matplotlib matplotlib.use('Agg') import matplotlib.pyplot as plt from matplotlib import animation from IPython.display import display, Image import time %matplotlib inline # Set common figure parameters newparams = {'figure.figsize': (14, 7), 'axes.grid': False, 'lines.markersize': 6, 'lines.linewidth': 2, 'font.size': 15, 'mathtext.fontset': 'stix', 'font.family': 'STIXGeneral'} plt.rcParams.update(newparams)
The gravitational pull between two objects is under classical conditions given by Newton's law of gravitation,$$ \vec{F}_{21}(t)=\vec{F}_{12}(t) = -\frac{Gm_1m_2}{{\vec{r_{12}}(t)}^3}\vec r_{12}, $$
where $m_1$ and $m_2$ are the masses of the two objects, $r$ is the distance between them and $G\approx 6.67\times 10^{-11} \,\text{m}^3/ \text{kg}\,\text{s}^2$ is the gravitational constant. Newton's law holds if it is assumed that the masses of the objects are isotropically distributed.
Consider a three body problem with three objects given by masses $m_1$, $m_2$ and $m_3$. By the principle of superposition, the gravitational pull on an object will be the sum of the gravitational pull of all the other objects $F_1 = F_{12} + F_{13}$. Thus, the equations of motion (EoM) of say $m_1$ is given by$$ \ddot{\vec{r}}_1(t) = -\frac{Gm_2}{\left[\vec{r}_{2}(t)-\vec{r}_{1}(t)\right]^3}\left[\vec{r}_{2}(t)-\vec{r}_{1}(t)\right]-\frac{Gm_3}{\left[\vec{r}_{3}(t)-\vec{r}_{1}(t)\right]^3}\left[\vec{r}_{3}(t)-\vec{r}_{1}(t)\right], $$$$ \dot{\vec{r}}_1(t)=\vec{v}_1. $$
The EoM in this problem is a set of ODEs. By giving two initial conditions, e.g. the starting velocity and position, we can reduce the problem to two ODEs, where the next step of the first ODE depends on the previous step of the second ODE. The right hand side (RHS) of the EoM can be described by the following function:
def RHS(t, y): """Calculate the RHS of the EoM, as described above.: z: array. Vector of length 12 holding the derivative of the current position and velocity (the velocity and acceleration) of the three object in the following manner: z = [vx1, vy1, vx2, vy2, vx3, vy3, ax1, ay1, ax2, ay2, ax3, ay3]. """ # Allocate a vector to hold the output values z = np.zeros(12) # Define initial velocities and distances between objects z[:6] = [y[6], y[7], y[8], y[9], y[10], y[11]] r21 = ((y[2] - y[0])**2.0 + (y[3] - y[1])**2.0)**0.5 r31 = ((y[4] - y[0])**2.0 + (y[5] - y[1])**2.0)**0.5 r32 = ((y[4] - y[2])**2.0 + (y[5] - y[3])**2.0)**0.5 # Pairwise forces Fx21 = G*m2*m1*(y[2] - y[0])/r21**3.0 Fy21 = G*m2*m1*(y[3] - y[1])/r21**3.0 Fx31 = G*m3*m1*(y[4] - y[0])/r31**3.0 Fy31 = G*m3*m1*(y[5] - y[1])/r31**3.0 Fx32 = G*m3*m2*(y[4] - y[2])/r32**3.0 Fy32 = G*m3*m2*(y[5] - y[3])/r32**3.0 # Accelerations z[6] = (Fx21 + Fx31)/m1 z[7] = (Fy21 + Fy31)/m1 z[8] = (-Fx21 + Fx32)/m2 z[9] = (-Fy21 + Fy32)/m2 z[10] = (-Fx31 - Fx32)/m3 z[11] = (-Fy31 - Fy32)/m3 return z
Since there are no forces or torques acting on the system (and no form of loss within the system), both the energy and the angular momentum stays constant. This provides a way to check if our calculations are sufficiently accurate. The kinetic energy, $K$, is given by$$ K=\frac{1}{2}m\vec v^2, $$
where $m$ is the mass and $v$ is the velocity. The potential energy $U$ between two objects is given by$$ U=-\frac{Gm_1m_2}{r_{12}}, $$
where $G$ is the gravitational constant, $m_i$ is the mass of object $i$ and $r$ is the distance between the two objects. The energies of the system can thus be calculated by:
def energy(z): """Calculate the mechanical energies of the three body system. Parameters: z: array. Vector of length 12 holding the current position and velocity of the three objects in the following manner: z = [x1, y2, x2, y2, x3, y3, vx1, vy1, vx2, vy2, vx3, vy3]. Returns: U: float. The potential energies of the system. K: float. The kinetic energies of the system. """ # Pairwise distance between objects r21 = ((z[2] - z[0])**2.0 + (z[3] - z[1])**2.0)**0.5 r31 = ((z[4] - z[0])**2.0 + (z[5] - z[1])**2.0)**0.5 r32 = ((z[4] - z[2])**2.0 + (z[5] - z[3])**2.0)**0.5 # Calculate potential energies # First object is "free", second object is moved from infinity to a distance r21 from the first object. # Third object is affected gravitationally by both objects. U1 = 0 U2 = -G*m1*m2/r21 U3 = -G*m1*m3/r31 - G*m3*m2/r32 U = U1 + U2 + U3 # Calculate kinetic energies of the three objects K1 = 0.5*m1*(z[6]**2 + z[7]**2) K2 = 0.5*m2*(z[8]**2 + z[9]**2) K3 = 0.5*m3*(z[10]**2 + z[11]**2) K = K1 + K2 + K3 return U, K
Furthermore, in this setup the absolute angular momentum $\vec L = \vec R\times m\vec v$ stays constant, and can be calculated by:
def angularMomentum(y): """Calculate absolute angular momentum of the three body system.: L1, L2, L3: array. Total absolute angular momentum of the system. """ L1 = m1*(y[0]*y[7] - y[1]*y[6]) L2 = m2*(y[2]*y[9] - y[3]*y[8]) L3 = m3*(y[4]*y[11] - y[5]*y[10]) return [L1, L2, L3]
We now implement the embedded Runge-Kutta pair (often called an adaptive Runge-Kutta method) to solve the EoM. In short, it is a scheme that uses two different Runge-Kutta methods of different order to get an estimate of the local truncation error. Thus, it is possible to more or less decide what accuracy we want the solution to have by adjusting the step size for each iteration. Another advantage of the adaptive step size method is that we achieve better accuracy where it is needed and lower accuracy where it is not (an example will follow). However, these methods may become more computationally demanding, and hence won't improve our implementation in every case.
The implementation can also be done with a constant step size method, which is done in the animation section below.
We are going to use the Runge-Kutta-Fehlberg order 4 / order 5 embedded pair (RKF45) as described in Adaptive Runge-Kutta Methods:
def ode45(f,t,y,h): """Calculate next step of an initial value problem (IVP) of an ODE with a RHS described by the RHS function with an order 4 approx. and an order 5 approx. Parameters: t: float. Current time. y: float. Current step (position). h: float. Step-length. Returns: q: float. Order 2 approx. w: float. Order 3 approx. """ s1 = f(t, y) s2 = f(t + h/4.0, y + h*s1/4.0) s3 = f(t + 3.0*h/8.0, y + 3.0*h*s1/32.0 + 9.0*h*s2/32.0) s4 = f(t + 12.0*h/13.0, y + 1932.0*h*s1/2197.0 - 7200.0*h*s2/2197.0 + 7296.0*h*s3/2197.0) s5 = f(t + h, y + 439.0*h*s1/216.0 - 8.0*h*s2 + 3680.0*h*s3/513.0 - 845.0*h*s4/4104.0) s6 = f(t + h/2.0, y - 8.0*h*s1/27.0 + 2*h*s2 - 3544.0*h*s3/2565 + 1859.0*h*s4/4104.0 - 11.0*h*s5/40.0) w = y + h*(25.0*s1/216.0 + 1408.0*s3/2565.0 + 2197.0*s4/4104.0 - s5/5.0) q = y + h*(16.0*s1/135.0 + 6656.0*s3/12825.0 + 28561.0*s4/56430.0 - 9.0*s5/50.0 + 2.0*s6/55.0) return w, q
To get some basis for comparison we will also use the Ordinary (fourth order) Runge-Kutta method, as described in Runge Kutta Method (this method will be used to make animations):
def rk4step(f, t, y, h): """Calculate next step of an IVP of an ODE with a RHS described by the RHS function with RK4. Parameters: f: function. Right hand side of the ODE. t: float. Current time. y: float. Current step (position). h: float. Step-length. Returns: q: float. Order 2 approx. w: float. Order 3 approx. """ s1 = f(t, y) s2 = f(t + h/2.0, y + h*s1/2.0) s3 = f(t + h/2.0, y + h*s2/2.0) s4 = f(t + h, y + h*s3) return y + h/6.0*(s1 + 2.0*s2 + 2.0*s3 + s4)
# Set gravitaional constant and masses. # The gravitaional constant is set to 1 for simplicity. G = 1. m1 = 1. m2 = 1. m3 = 1. # Period of calculations T = 5 # Tolerance TOL = 0.00001 # Maximum number of steps maxi = 1000 # "Protector-constant" for small w theta = 0.001 # Number of steps (RK4) n = 1000 # Different initial conditions to try out, on the form # y = [x1, y2, x2, y2, x3, y3, vx1, vy1, vx2, vy2, vx3, vy3] # z0 = [2., 2., 0., 0., -2., -2., 0.2, -0.2, 0., 0., -0.2, 0.2] # z0 = [-0.970, 0.243, 0.970, -0.243, 0., 0., -0.466, -0.433, -0.466, -0.433, 2*0.466, 2*0.433] # z0 = [2., 0., -2., 0., 0., 0., 0., -0.6, -0.6, 0., 0., 0.] z0 = [1., 0.000001, -1., 0., 0., 0., 0., -0.4, 0., 0.4, 0., 0.]
We are now ready to perform the calculations and plot the results. To get a feel for the problem, you should run the notebook yourself and try out different initial conditions $z_0$. E.g., for the last $z_{0}$ listed above, if you set $y_{2} = 0$ instead of, say, $0.000001$, the orbits are stable. As we will see below, the three body system is highly sensitive to the initial conditions.
# First step and initial time h = T/n t = 0. # Allocate matrices and fill with initial conditions Z = np.zeros((12, maxi + 1)) Z[:, 0] = z0 E = np.zeros((maxi + 1, 2)) E[0, :] = energy(z0) L = np.zeros((maxi + 1, 3)) L[0, :] = angularMomentum(z0) # Declare iteration integer i = 0 e=1. # Perform ode45 calculations tic = time.time() while (t < T) & (i < maxi): w, q = ode45(RHS, t, Z[:, i], h) e = max(abs((w - q)/np.maximum(w, theta))) if e > TOL: h = 0.95*(TOL*e)**(1/5)*h w, q = ode45(RHS, t, q, h) e = max(abs((w - q)/np.maximum(w, theta))) while e > TOL: h = h/2. w, q = ode45(RHS, t, q, h) e = max(abs((w - q)/maximum(w, theta))) if e < 0.1*TOL: h = h*2. Z[:, i+1] = q E[i+1, :] = energy(Z[:, i+1]) L[i+1, :] = angularMomentum(Z[:, i+1]) t += h i += 1 print("%.5f s, run time of adaptive RK45 method." % (time.time() - tic)) # Print number of steps used if (i == maxi): print('%i, maximum number of steps reached by adaptive RK45 method.' % i) else: print('%i, steps used by adaptive RK45 method.' % i)
0.16208 s, run time of adaptive RK45 method. 999, steps used by adaptive RK45 method.
# Plot result plt.figure() # Position plt.subplot(2, 2, (1, 3)) plt.plot(Z[0, 0:i], Z[1, 0:i], '-r', label='m1') plt.plot(Z[2, 0:i], Z[3, 0:i], '-b', label='m2') plt.plot(Z[4, 0:i], Z[5, 0:i], '-g', label='m3') plt.plot(Z[0, 0], Z[1, 0], '*r', label='Initial position m1') plt.plot(Z[2, 0], Z[3, 0], '*b', label='Initial position m2') plt.plot(Z[4, 0], Z[5, 0], '*g', label='Initial position m3') plt.xlabel('x') plt.ylabel('y') plt.legend(loc='best') plt.title('Trajectories') # Mechanical energy plt.subplot(2, 2, 2) plt.plot(E[0:i, 0], 'g', label='K') plt.plot(E[0:i, 1], 'b', label='U') plt.plot(E[0:i, 0] + E[0:i ,1], 'm', label='Total mechanical energy E') plt.ylabel('E') plt.legend(loc='best') plt.title('Mechanical energy and absolute angular momentum') # Angular momentum plt.subplot(2, 2, 4) plt.plot(L[0:i, 0], 'r', label='m1') plt.plot(L[0:i, 1], 'b', label='m2') plt.plot(L[0:i, 2], 'g', label='m3') plt.plot(L[0:i, 0] + L[0:i, 1] + L[0:i, 2], 'm', label='Total L') plt.xlabel('Steps, i') plt.ylabel('L') plt.legend(loc=3) plt.show()
With the initial conditions $z_0$ chosen above the three body system is unstable, hence $m_2$ drifts off by itself while $m_1$ and $m_3$ engages in a tight dance together. Furthermore, the total angular momentum $L$ and the total mechanical energy $E$ are fairly constant throughout the calculation, indicating sufficiently accurate calculations.
This method often require few steps. As a consequence, the plot might seem somewhat poor, even though the accuracy might be high. Using the RK4 method without adapting the step size to the tolerance, we get a different picture.
# Set constant step size h = T/n # Set initial time t = 0. # Allocate matrices and fill with initial conditions Z2 = np.zeros((12, n+1)) Z2[:, 0] = z0 E2 = np.zeros((n+1, 2)) E2[0, :] = energy(z0) L2 = np.zeros((n+1, 3)) L2[0, :] = angularMomentum(z0) tic = time.time() for i in range(0, n): Z2[:, i+1] = rk4step(RHS, t, Z2[:, i], h) E2[i+1, :] = energy(Z2[:, i+1]) L2[i+1, :] = angularMomentum(Z2[:, i+1]) t += h print("%.5f s, run time of RK4 method, with %i steps."% (time.time() - tic, n))
0.07742 s, run time of RK4 method, with 1000 steps.
# Plot result plt.figure() # Position plt.subplot(2, 2, (1, 3)) plt.plot(Z2[0, 0:i], Z2[1, 0:i], '-r', label='m1') plt.plot(Z2[2, 0:i], Z2[3, 0:i], '-b', label='m2') plt.plot(Z2[4, 0:i], Z2[5, 0:i], '-g', label='m3') plt.plot(Z2[0, 0], Z2[1, 0], '*r', label='Initial position m1') plt.plot(Z2[2, 0], Z2[3, 0], '*b', label='Initial position m2') plt.plot(Z2[4, 0], Z2[5, 0], '*g', label='Initial position m3') plt.xlabel('x') plt.ylabel('y') plt.legend(loc='best') plt.title('Trajectories') # Mechanical energy plt.subplot(2, 2, 2) plt.plot(E2[0:i, 0], 'g', label='K') plt.plot(E2[0:i, 1], 'b', label='U') plt.plot(E2[0:i, 0] + E2[0:i, 1], 'm', label='Total mechanical energy, E') plt.ylabel('E') plt.legend(loc='best') plt.title('Mechanical energy and absolute angular momentum.') # Angular momentum plt.subplot(2, 2, 4) plt.plot(L2[0:i, 0], 'r', label='m1') plt.plot(L2[0:i, 1], 'b', label='m2') plt.plot(L2[0:i, 2], 'g', label='m3') plt.plot(L2[0:i, 0] + L2[0:i, 1] + L2[0:i, 2], 'm', label='Total L') plt.xlabel('Steps, i') plt.ylabel('L') plt.legend(loc='best') plt.show()
It is obvious from taking a glance at the total mechanical energy $E$ and the total angular momentum $L$ that this calculation is flawed. We cannot trust the trajectories the ordinary fourth order Runge-Kutta (RK4) method produced with just a 1000 steps. In comparison, the adaptive Runge-Kutta (RK45) method performed better using only 224 steps, though it approximately doubled the execution time. Now, if we use an initial number of steps $n$ = 10 000, the ordinary RK4 method yields plausible trajectories (try for yourself). However, the adaptive RK45 method produce the same results in approximately the same number of steps as before, thus keeping its execution time low in comparison.
The easiest way to create an animation is to use a constant step size function, such as the fourth order Runge-Kutta method (the last run computation will be animated). We are now going to animate the previous computations with $n$ = 10 000. The animation in the introduction was made with the following code:
# Set up the figure fig = plt.figure() ax = plt.axes(xlim=(np.min(Z2[[0,2,4],:]), np.max(Z2[[0,2,4],:])), ylim=(np.min(Z2[[1,3,5],:]), np.max(Z2[[1,3,5],:]))) ax.set_aspect('equal') # Define the different elements in the animation tail1, = ax.plot([],[],'r') # Tail obj. 1 tail2, = ax.plot([],[],'b') # Tail obj. 2 tail3, = ax.plot([],[],'g') # Tail obj. 3 obj1, = ax.plot([],[],'ro') # Obj. 1 obj2, = ax.plot([],[],'bo') # Obj. 2 obj3, = ax.plot([],[],'go') # Obj. 3 # Calculates the number of frames FPS = 15 framesNum = int(FPS*T) # Animation function. This is called sequentially. def animate(j): i = j*int(n/framesNum) obj1.set_data(Z2[0,i],Z2[1,i]) obj2.set_data(Z2[2,i],Z2[3,i]) obj3.set_data(Z2[4,i],Z2[5,i]) tail1.set_data(Z2[0,0:i],Z2[1,0:i]) tail2.set_data(Z2[2,0:i],Z2[3,0:i]) tail3.set_data(Z2[4,0:i],Z2[5,0:i]) # Create animation anim = animation.FuncAnimation(fig, animate, frames=framesNum) # Save animation # If this don't work for you, try using the another writer (ffmpeg, mencoder, imagemagick), # or another file extension (.mp4, .gif, .ogg, .ogv, .avi etc.). Make sure that you have # the codec and the writer installed on your system. anim.save('ThreeBodyProblem.gif', writer='imagemagick', fps=FPS) # Close plot plt.close(anim._fig) # Display the animation with open('ThreeBodyProblem.gif','rb') as file: display(Image(file.read())) | https://nbviewer.org/urls/www.numfys.net/media/notebooks/planetary_motion_three_body_problem.ipynb | CC-MAIN-2022-33 | refinedweb | 3,073 | 61.22 |
I have this header file in my project:
#ifndef COMMONINCLUDES_H
#define COMMONINCLUDES_H
#include "utilities.h"
#include "textOutput.h"
#include "game.h"
class Player
{
public:
int score;
int poX, posY;
};
#endif // COMMONINCLUDES_H
#include <commonincludes.h>
void turn(Player *currplayer, int mapSize);
You have circular header inclusion.
game.h includes
commonincludes.h and
commonincludes.h includes
game.h. Your include guards break the infinite inclusion cycle, but they break it at the point where
Player remains undeclared at the point of
turn declaration.
Judging by what you posted so far, there's no need for
#include "game.h" in
commonincludes.h. What it is doing there?
P.S. Use
#include "..." for including your own header files. The
#include <...> syntax is for standard headers. | https://codedump.io/share/ZeclZ7P58APd/1/variable-of-field-declared-void-error-when-trying-to-use-object-of-custom-class | CC-MAIN-2017-04 | refinedweb | 121 | 55.2 |
STAFF HANDBOOK YWAM HARPENDEN
TABLE OF CONTENTS
YWAM INTERNATIONAL ......................................................................................................................5 STATEMENT OF FAITH............................................................................................................................................ 6 WHAT IS A YWAMer? ............................................................................................................................................... 6 THE FOUNDATIONAL VALUES OF YWAM....................................................................................................... 7 YWAM HARPENDEN............................................................................................................................ 10 VISION .......................................................................................................................................................................... 11 MISSION....................................................................................................................................................................... 11 CORE VALUES ........................................................................................................................................................... 11 GOALS........................................................................................................................................................................... 12 HIGHFIELD OVAL & YWAM HARPENDEN HISTORY ................................................................. 13 WORKING AT YWAM HARPENDEN ................................................................................................ 16 OVERVIEW OF YWAM HARPENDEN .............................................................................................................. 17 LEADERSHIP GROUPS........................................................................................................................................... 18 MEETING TOGETHER as a WHOLE ................................................................................................................. 18 THE WEEK AT A GLANCE .................................................................................................................................... 19 YWAM HARPENDEN CALENDAR 2014 ......................................................................................................... 20 MAP OF YWAM HARPENDEN ............................................................................................................................ 21 HISTORY / PURPOSE OF ‘AT HOME DAYS’ & COMMUNITY DAYS..................................................... 22 ID (Staff Development) ......................................................................................................................................... 23 HOLIDAYS, FURLOUGHS & TIME AWAY GUIDELINES............................................................................ 23 FAMILY LIFE.............................................................................................................................................................. 25 YWAM ENGLAND and Western Europe ........................................................................................ 28 YWAM England & Wales....................................................................................................................................... 29 YWAM WESTERN EUROPE ................................................................................................................................. 30 IMPORTANT LEGAL INFORMATION AND REQUIREMENTS ................................................... 31 REGISTERING FOR TAXES – THE BASICS..................................................................................................... 32 VISA INFORMATION .............................................................................................................................................. 35 PERSONAL FINANCES ......................................................................................................................... 37 MONEY, BANKS, AND SETTING UP A BANK ACCOUNT.......................................................................... 38 SUPPORT RAISING.................................................................................................................................................. 40 GUIDELINES FOR STAFF FEE DEBT................................................................................................................ 41 HIGHFIELD OVAL OPERATIONS...................................................................................................... 43 QUARTERLY COMMUNITY ROTAS .................................................................................................................. 44 FACILITIES BOOKING............................................................................................................................................ 44 PETS .............................................................................................................................................................................. 44 INSURANCE................................................................................................................................................................ 44 RUBBISH & RECYCLING (Updated May 2011) ........................................................................................... 45 WASTE COLLECTION FROM HIGHFIELD OVAL......................................................................................... 46 MAINTENANCE & GROUNDS ............................................................................................................................. 48 SECURITY.................................................................................................................................................................... 50 HOSPITALITY ............................................................................................................................................................ 52 FIRE SAFETY.............................................................................................................................................................. 55 RECEPTION ................................................................................................................................................................ 57 TELEPHONES ............................................................................................................................................................ 58 FACILITIES on the Oval......................................................................................................................................... 61 FACILITIES OPEN TO THE PUBLIC.................................................................................................................. 62 THE BRAMLEY HALL ............................................................................................................................................. 64 STAFF POLICY FOR EATING IN THE BRAMLEY HALL ............................................................................ 64 HOUSING................................................................................................................................................. 67 GUIDELINES FOR LIVING ON THE OVAL ...................................................................................................... 68 HOUSING FEES ......................................................................................................................................................... 68 YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 2
CRITERIA FOR HOUSING ALLOCATION ........................................................................................................ 69 HOUSING GROUP ..................................................................................................................................................... 69 DEFINITION OF OTHER ROLES INVOLVED IN HOUSING ALLOCATION......................................... 70 ADDITIONAL HOUSING INFORMATION........................................................................................................ 72 WHAT CAN BE EXPECTED IN SHARED ACCOMMODATION ................................................................ 72 WHAT CAN BE EXPECTED IN SELF-‐CONTAINED ACCOMMODATION? .......................................... 73 PAINT POLICY ON THE OVAL ............................................................................................................................ 73 REFURBISHMENT GROUP ................................................................................................................................... 74 EMERGENCIES AND REPAIRS............................................................................................................................ 75 LOCAL TRANSPORT ............................................................................................................................ 77 DRIVING & CARS...................................................................................................................................................... 78 TRAINS & TRAIN TRAVEL ................................................................................................................................... 80 LOCAL BUSES ............................................................................................................................................................ 81 LONG-‐DISTANCE COACHES ................................................................................................................................ 81 TAXIS............................................................................................................................................................................. 82 HITCH-‐HIKING (GETTING A LIFT)................................................................................................................... 82 HEALTH, DENTAL & MEDICAL......................................................................................................... 83 EMERGENCY SERVICES & MEDICAL CARE .................................................................................................. 84 HEALTH & MEDICAL INFORMATION ............................................................................................................. 84 MINOR INJURIES UNITS ....................................................................................................................................... 84 ACCIDENT & EMERGENCY (A & E) .................................................................................................................. 85 LOCAL CHURCH FELLOWSHIPS....................................................................................................... 87 HARPENDEN & THE LOCAL AREA................................................................................................................... 92 HARPENDEN.............................................................................................................................................................. 93 TOWNS AND CITIES NEARBY ............................................................................................................................ 93 MAP OF HARPENDEN............................................................................................................................................ 95 LIVING IN BRITAIN.............................................................................................................................. 96 BRITISH CULTURE .................................................................................................................................................. 97 EATING AND DIET ............................................................................................................................................... 100 IF YOU ARE INVITED OUT ................................................................................................................................ 101 HOLIDAYS, SEASONS AND TIME ................................................................................................................... 103 SHOPPING................................................................................................................................................................ 105 SHOPPING IN HARPENDEN ............................................................................................................................. 106 SECOND HAND GOODS ...................................................................................................................................... 107 SHOPPING OUTSIDE OF HARPENDEN ........................................................................................................ 107 MORE TO DO, SEE & KNOW ............................................................................................................................. 108 APPENDIX ............................................................................................................................................110 REVIEW DATES ..................................................................................................................................................... 111 TO DO LIST:............................................................................................................................................................. 111 GUIDELINES ON DRINKING ALCOHOL AT YWAM HARPENDEN .................................................... 112 SMOKING.................................................................................................................................................................. 113 SUBSTANCE / DRUG ABUSE ............................................................................................................................ 113 FIDELITY: KEEPING COMMITMENTS.......................................................................................................... 114 NOTES FOR REGISTRATION WITH THE INLAND REVENUE FOR INCOME TAX & NATIONAL INSURANCE............................................................................................................................................................. 115 INFORMATION FROM THE HMRC WEBSITE ........................................................................................... 116 SELF-‐EMPLOYED TAX AND NATIONAL INSURANCE ..................................................................116 INCOME TAX AND SELF ASSESSMENT ...................................................................................................... 116 PERSONAL ALLOWANCE .................................................................................................................116 Levels of Personal Allowance.......................................................................................................................... 117 Class 2 National Insurance contributions .................................................................................................. 117 RECORD KEEPING................................................................................................................................................ 117 Sample Letter to send to HMRC for registering for National Insurance & as being self-‐ employed.................................................................................................................................................................. 122 PROCEDURES FOR OVAL SECURITY CHECK ............................................................................................ 123 YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 3
Holiday & Time Away Request Form............................................................................................................125 YWAM HARPENDEN FACILITIES REQUEST FORM ................................................................................126 LOCAL SCHOOLS AND HOW TO APPLY .......................................................................................................127 DEPARTING YWAM HARPENDEN -‐ A CHECKLIST .................................................................................129 ROOM /HOUSE CHECK OUT FORM ...............................................................................................................130 YWAM England Safeguarding Procedure....................................................................................................131 SAFEGUARDING GUIDELINES FOR All YWAM ENGLAND STAFF AND TRAINEES...................131 YWAM England Safeguarding Team and Other Important Contact Numbers..........................132 (List to be updated as necessary)...................................................................................................................132 Please fill in telephone numbers for your location.................................................................................132 Safeguarding Team ...............................................................................................................................................132 YWAM ENGLAND SAFEGUARDING POLICY ..............................................................................................133 PROTECTING YOUNG PEOPLE AND VULNERABLE ADULTS.............................................................133 AND APPOINTING WORKERS ..........................................................................................................................133 APPENDIX A .............................................................................................................................................................153 Supplementary Documents to YWAM England Safeguarding Policy..............................................153 These documents should be used alongside YWAM-England’s safeguarding policies and practices.....................................................................................................................................................................153 Safeguarding Information for All Staff and Students.............................................................................154 Serving with Youth With A Mission England.............................................................................................154 Statement of Adult Acting In Loco Parentis................................................................................................157
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 4
YWAM INTERNATIONAL
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 5
STATEMENT OF FAITH Youth With A Mission (YWAM) is an international movement of Christians from many denominations, dedicated to presenting Jesus Christ personally to this generation. We aim to mobilise as many people as possible to help in this task and to train and equip believers for their part in fulfilling the Great Commission. As citizens of God’s Kingdom we are called to love and serve His Body, the Church; and to present the whole Gospel for the whole man throughout the world. We of Youth With A Mission believe that: • The Bible is God’s inspired and authoritative Word, revealing that Jesus Christ is God’s Son and that man is created in God’s image. • God created us to have eternal life through Jesus Christ. • Although all men have sinned and come short of God’s glory, God has made salvation possible through the death on the cross and resurrection of Jesus Christ. • Repentance, faith, love and obedience are fitting responses to God’s initiative of grace towards us. • God desires all men to be saved and to come to knowledge of the truth. • The Holy Spirit’s power is demonstrated in and through us for the accomplishing of God’s command: “Go into all the world and preach the good news to all creation.” (Mark 16:15 NIV) • Youth With A Mission leaders joined Christian leaders from around the world in 1974 in the signing of the Lausanne Covenant, further clarifying our beliefs as a mission.
WHAT IS A YWAMer?
Serving in YWAM is a calling/vocation rather than a place of work, and can therefore be viewed more as an alternative way of life than an organization we work for. Our values reiterate the sense of our identity or "DNA" rather than our job description. YWAM also affirms the importance of families serving God together in missions, with each member sharing the call to missions and contributing their gifts in unique and complementary ways. The norm for YWAM communities is that families are as fully involved in the vision and activities of the mission as possible. Husbands, wives and children are all valued as part of the YWAM family and share as much in the responsibilities as in the privileges of belonging. Parents of children under school age would clearly not be expected to get as involved in ministry to the same degree as parents with children at school, but we do place a high value on every member of the Oval community making a contribution to the life and ministry of YWAM both in terms of the running of the campus as well as outreach. All YWAM staff, including families, will be encouraged to get involved in outreach / evangelism initiatives during the course of a year; either in an on-‐going local effort or going away for a period of outreach.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 6
THE FOUNDATIONAL VALUES OF YWAM -‐-‐making. HARPENDEN STAFF HANDBOOK (Edited April 2013) page, centred-‐STRUCTURED AND DECENTRALIZED YWAM is broad-‐structured honour honours the gifts and callings of those under his/her care and guards their rights and privileges. Just as Jesus served His disciples, we stress the importance of those with leadership responsibilities serving those whom they lead.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 8
12. DO FIRST, THEN TEACH YWAM is committed to doing first, then teaching. We believe that firsthand experience gives authority to our words. Godly character and a call from God are more important than an individual's gifts, abilities and expertise. 13. BE RELATIONSHIP-‐ORIENTED YWAM is dedicated to being relationship-‐oriented honouring God-‐given. (YWAM Foundational Values approved by the Global Leadership Team December 2010.) YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 9
YWAM HARPENDEN
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 10
It all started when a 20-‐year-‐old student, Loren Cunningham, opened his Bible and asked God to speak into his mind in prayer. As he lay back in his bed and looked up, he saw a “mental movie” — waves on a map, crashing onto the shores. Then, as he watched, the waves turned into young people, going to every continent and sharing the good news about Jesus. “Was that really you, Lord?” he asked. This radical dream -‐ that young people could be missionaries -‐ remained. Four years later, in 1960, he started a movement with that idea encapsulated in its name: Youth With A Mission (YWAM). The story of how YWAM began and grew is a story of God’s direction and God’s grace in using ordinary people from all over the world. Join us at YWAM Harpenden, one of the places where the story continues, and together let’s see God’s dreams become reality.
VISION YWAM Harpenden is a Multiplier for the Kingdom of God, equipping and releasing waves of young people who live like Jesus and transform the nations.
MISSION We are a multi-‐generational, international mission community which: • Engages in strategic prayer as the primary initiator of change. • Pioneers initiatives, which explore new ways to impact our world with the Gospel. • Supports local, national and international YWAM ministries and the Church through relationships, communications and resources. • Develops and multiplies training that will equip people to transform nations. • Directs our outreach towards the unreached and poor through ministries of evangelism, compassion and reconciliation.
CORE VALUES Empowered by the Holy Spirit we commit to live as Jesus lives, displaying: • Radical LOVE for God • God at the heart of our personal and community life through prayer, worship and obedience to His Word. • Extravagant LOVE for one another • Gracious LOVE for those who come among us • Passionate LOVE for the lost • Sacrificial LOVE for the World • As a welcoming community we celebrate diversity, joyfully embracing all those that God brings to us. • We seek out and respond enthusiastically to opportunities, individually and corporately, to bring people to Jesus. • Compelled by Christ’s compassion, we take responsibility to bring healing and transformation to a broken world. • Our life together is characterised by the fruit of the Spirit, expressed in unity, generosity and sacrificial living guarded by mutual accountability and godly leadership.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 11
GOALS In response to the prophetic word received by the GLT in 2000, ‘Crossing the Jordan’ and the prospect of growth with up to 200,000 joining the mission () we recognize that as YWAM Harpenden we need to be preparing for growth which will require a flexibility and quick responsiveness to the Lord. This may be more of a spiritual and cultural shift than we realize. The intention is to be poised to “Go”, and be prepared for the next wave. In this season, the primary goals of YWAM Harpenden are:
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 12
HIGHFIELD OVAL & YWAM HARPENDEN HISTORY 1869: a young Methodist minister Thomas Bowman Stephenson, together with fellow Methodists Alfred Mager and Francis Horner, started the “National Children’s Home” in London. This was a step of faith, prompted by their evangelistic compassion for the countless homeless children who begged and stole to survive on the streets of London. 1908: Highfield Oval is part of a large farm estate purchased by The National Children’s Home (NCH). It is to be developed into a self-‐contained complex to provide a home for homeless children. This step of faith prompted by evangelistic compassion led to the largest branch of the NCH in the country. 1910: “Elmfield” in Ambrose Lane, Harpenden, now a Christian school called The King’s School, opened as a sanatorium for children with tuberculosis. Shortly afterwards, work began on the building of Highfield Oval. 1912: Work began on the building of Highfield Oval with large residential units as well as training and administrative buildings. 1928: The present Chapel is built to replace a temporary chapel. 1933: There are four blocks of houses for girls, and six for boys, altogether some 320. In addition to a basic education, each child receives training in a trade: boys in printing, joinery, boot repair, painting and decorating, gardening and farming; girls in housework, office work, teaching, or as children’s nurses. Highfield Oval functioned successfully for many decades as a more-‐or-‐less self-‐contained community, having its own school, bakery, and printing works. The children were looked after by ‘Sisters’, a Methodist Order of dedicated women who took on care of the children as their life’s work. The concept was that the children should be cared for in a family setting. Each ‘family’ had two Sisters who looked after them. Later, they sometimes had house-‐parents. Over 50,000 children were brought up in various branches of the National Children’s Home. Several retired Sisters and other former staff still live in Harpenden, as well as many of the children who were brought up at the Oval. Former “children” of the Home often return, sometimes from far afield, to visit “The Oval” where they grew up. Eventually due to changes in childcare, funding, etc., the Children’s Home was used less and less. It became policy to set up smaller family units in the community. By 1983, the Home was almost empty, except for some administrative functions. 1983: Some leaders and staff of Youth With A Mission, until then based in Sussex, had moved to temporary housing in London, seeking a permanent centre there. After 2 ½ years of searching, no suitable property had been found for a permanent administrative centre, although there were various teams working in different parts of London. Finally, things came to the point where the team who had moved up from Sussex in faith had to leave their temporary accommodation within a month. 1985: The YWAMers in London expressed to the Lord their willingness to move out of London if, contrary to what they had thought, He had another place for them. But where should they start looking with such limited time? 1986: The group prayed that if they were to move to a different area, God would bring the right place to their attention. A few days later they heard about Highfield Oval, and came to see it. There was just the right mixture of accommodation for families and single people, and just the right amount of office space. They leased a small portion of the unused parts of the site and moved in three weeks later, at the beginning of March 1986. The potential for training and ministry was increasingly evident. Soon it became clear why the Lord had brought YWAM, unexpectedly, to this site. Over the next years the team grew from the initial 40 staff to some 130 adults and children. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 13
Enquiries were made about possible purchase or long-‐term lease of the property. However, at the time, the owners were hoping to secure a change of planning status so that the site could be sold for major housing development. 1993: For seven years YWAM rented part of the site, praying and negotiating for purchase. During this time the property was held on a very insecure footing, on very short-‐term leases. There were many battles in prayer, and hard work to be done, before the Lord finally enabled YWAM to purchase the property for £2.1 million in March 1993. It seemed nothing short of a miracle; firstly that the property was offered for sale, and secondly that the money became available for the purchase. This came about through the sacrificial giving of YWAM staff around the world in a “Loaves and Fishes Offering,” the generosity of friends of YWAM, a bank loan and a loan from a Christian Trust. At the same time there was a transfer from YWAM Amsterdam of a large ministry dedicated to Frontier Missions as 20 staff and their dependents joined Highfield Oval. 1994: The Highfield Oval Christian Preschool opens for the benefit of staff children and non-‐ YWAM children. Eventually the running of the Preschool was turned over to the nearby King’s School. They run a very successful programme with a permanent waiting list and excellent ratings from the governmental watchdog agency OFSTED. Cell UK, exploring the cell model in the local church, is launched. No fewer than 300 delegates come to the Oval twice a year for training and fellowship. 1995: Mercy Ships opens its first UK office at Highfield Oval. 1996: First Arts Festival 1997: The ECO Programme starts; it is designed to help Non-‐Western missionaries prepare for missions in a foreign country, help them adjust to life in a cross-‐cultural environment and learn English at the same time. 1998: In September, the first ‘At Home’ Week takes place. During that week God gave us a vision for the Factory to be used as a training centre for young people. As a step of faith we removed all the furniture stored there, had a great clear out and held the Love Feast there, in spite of broken windows and a leaky roof. With no electricity, the candlelight gave a great atmosphere and helped us see it with eyes of faith! In November, the Factory team and building were launched by holding the first “Gathering” of DTS students from all the campuses in England and Scotland, as well as a couple of European locations. 1999: Mercy Ships UK, based at Highfield Oval, is instrumental in the purchase of a Danish Vessel renamed ‘Africa Mercy’. 2000 /2001: The first of two Argentinean summer gatherings were held, drawing on the South American revival. 2002: Business as Mission opens an office. The words may not necessarily be ones we are used to hearing in the same sentence, but they represent a powerful trend in the body of Christ and YWAM. Business for support and business development for social transformation is among key BAM areas. 2003: Centre for International Justice and Reconciliation (CIJR) attains Special Consultative Status at the United Nations as YWAM England’s public policy branch. Marine Reach England and the European office of YWAM’s Marine Reach International are launched. 2004: YWAM’s international leadership team (GLT) hold their annual meeting at Harpenden to commission Lynn Green, Iain Muir and John Dawson as the International Leaders. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 14
2005: “Transformation” takes place during the summer, a joint effort with our 40 Days programme and the prayer network of 24/7, bringing a total of 350 young people here for a long weekend being challenged for missions. “Re-‐Engage” – another joint effort with 40 Days, bringing past YWAMers from their jobs to the Oval for a fortnight to be re-‐inspired by the Great Commission in their areas of influence. During At Home Days, teams come from New Song and Destiny City churches to minister to us. 2006: ‘Orphans kNOw More’ started. Foundations in Intercultural studies, a UofN course started. We celebrated 20 years of YWAM Harpenden and the last of the buildings on the Oval renovated, with people able to live in both sides of building #8. YWAM England enters into 40 weeks of prayer and fasting and a Re-‐Engage summer event. In September of that year, following the GLT at YWAM Harpenden, YWAM England gathered together at Holmsted Manor with Loren & Darlene Cunningham, John Dawson and Dr. Atef. This was a poignant time as we gave in an offering towards the purchase of the Marine Reach ship The Next Wave, the “cork out of the bottle” for the next season of ministry for Youth With A Mission. 2007: John & Suzi Peachey appointed as leaders of YWAM Harpenden. We had the first DTS on The Next Wave. Beijing to London, a prayer ministry focusing on raising up a missions movement between these Olympic cities and their games, is formed. 2008: Oval Café opens. Fit Mums starts. School of Reconciliation and Justice (SORJ) pioneered. DTS Centre established at YWAM Harpenden. 2009: ‘Forever 2012’, the Olympic Outreach team established. Humanities and International Studies Course run at YWAM Harpenden. 2010: The training Department pioneers 3 new schools: School of Design (SOD), Documentary Filmmaking School (DFS) and School of Web Design & Communication (SWDC). YWAM 50th Anniversary Celebration is held at YWAM Harpenden with over 800 people visiting and staying on site, in tents, on floors and wherever else we can put them! 2011: Foundations in Community Development School (FCD) pioneered and School of Event Management (SEM) run for the first time at YWAM Harpenden. We have a twenty-‐fifth Anniversary celebration of YWAM Harpenden in June. The work which is done here, and the training that is given, is touching the farthest places of the earth, as well as the needs of this nation. The whole community, including staff, and trainees, is in the region of 240 people. Much restoration and refurbishment has taken place, often with voluntary help, but much more remains to be done. We look forward to the day when the old factory building can house our “community centre”: a restaurant, library, bookshop, offices, fitness centre and other community facilities. 2012: As London hosted the Olympics, YWAM Harpenden hosted seven events during the summer events including Circuit Riders (two weeks of evangelism for young people), a Sports and Arts festival (Go for Glory), two weeks of outreaches during the Olympic Games and the GLG (Global Leadership Gathering) 2013: Carl Tinnion (YWAM England Director) and Dale Lambert were appointed to lead a transition leadership team as John and Suzi Peachey stepped out of base leadership.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 15
WORKING AT YWAM HARPENDEN
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 16
OVERVIEW OF YWAM HARPENDEN This is an illustration of the ministries at YWAM Harpenden, not an organisational diagram. Facilitate • Catering • Maintenance & Grounds • Hospitality & Oasis Flat • Accounts
Outreach
• • • • • • • • •
• • • • • • •
Site Improvement Personnel Mission Builders National Support Communications Oval Operations IT
Orphans Know More Marine Reach Oval Café Schools Ministry Sports Oasis Centre Mums & Tots in Luton Batchwood The Next Wave
• • • • • •
London Newcastle Manchester Cornwall Bristol Luton
• • • •
Pioneer
• • • •
•
Train Seminars Discipleship Training Schools School of Design Foundations of Intercultural Studies Documentary Filmmaking School Humanities and International Studies School of Web Design & Communication Foundations of Community Development ID – Staff Development
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 17
LEADERSHIP GROUPS Leadership Team The Leadership Team provides the strategic direction for YWAM Harpenden, meeting weekly to pray and discuss various issues. Management Team The Management Team consists of many of our ministry leaders and makes practical decisions regarding the running of the campus. They meet on a weekly basis. Training Core Team This group decides the direction of our training ministry and also makes practical decisions pertaining to our training schools.
MEETING TOGETHER as a WHOLE
The following corporate meetings are all in the Chapel (unless otherwise communicated) and are for everyone to attend. Intercession: through Fasting, Worship & Prayer Monday; 12:45-‐14:00 Community Meeting Tuesday evening; 19:20 for coffee, to start at 19:30, aiming to finish by 21:30; sometimes we’re having such a great time that we stay after the meeting has officially finished..... Worship and celebration Reports Teaching Prayer This is for the whole community, including your children and young people. It is also open to people who are friends of YWAM, visitors and local Christians. Staff Meeting Tuesday afternoon, 14:00; this meeting aims to be finished by 15:00 Testimonies Communications from the various teams Reports Prayer for incoming and outgoing staff
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 18
THE WEEK AT A GLANCE Formal Office Hours (Monday-Friday) 09:00 Start of formal office hours 09:00 -‐ 09:15 Prayer* taken from the Scriptures (in the Chapel) 13:00 Lunch in the Bramley Hall 17:30 End of formal office hours 18:00 Dinner in the Bramley Hall These hours are guideline times. Several staff on the campus work part-‐time or flexi-‐time or your team may not function within working hours, such as doing church-‐based ministry or youth ministry that doesn’t happen during usual work hours. Discuss this with your team leader for guidance on how to manage your time in these circumstances. Please be aware that there may be times that you are expected to work on the weekends, such as campus events that happen on the weekend. MEAL TIMES IN THE BRAMLEY HALL Monday–Friday Breakfast 07:45 – 08:15 (breakfast cleared away at 08:15) Lunch 13:00 (except for Monday when we have fasting) Dinner 18:00 Saturday & Sunday Breakfast / Lunch 08:30-‐09:30 Dinner 18:00
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 19
YWAM HARPENDEN CALENDAR 2014 WINTER QUARTER Winter DTS/School of Design begins Staff Orientation Community Days Chinese Training Seminar Weekend SPRING QUARTER Staff Orientation Easter Festival School of Design Graduation Spring DTS/School of Music in Missions begins Good Friday (Public Holiday) Easter Monday (Public Holiday) TESOL begins Early May Bank Holiday (Public Holiday) Spring Bank Holiday (Public Holiday) TESOL graduation YWAM England Staff Gathering Winter DTS Graduation SUMMER QUARTER Summer DTS/SWDC/DFS begins Summer BBQ/Open Day Staff Orientation Marriage Seminar Singles Seminar Family Camp Summer Bank Holiday (Public Holiday) AUTUMN QUARTER Staff Orientation At Home Days Spring DTS Graduation School of Web Design & Communications Graduation Documentary Film School Graduation Autumn DTS/Crossroads/FCD/HIS begins Apple Festival Summer DTS Graduation School of Humanities and International Studies Graduation
January 13th January 13th – 17th January 20th & 21st March 7th – 9th March 31st – April 4th April 5th (To Be Confirmed) April 4th April 7th April 18th April 21st April 21st May 5th May 26th May 30th May 30th – June 1st June 18th June 30th July 5th (To be Confirmed) July 7th – 11th August 11th – 15th August 18th – 20th August 22nd – 27th August 25th September 8th – 12th September 16th – 20th September 17th September 26th September 26th September 29th October 11th December 10th December 19th
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 20
MAP OF YWAM HARPENDEN
1
Building No1 – Staff Housing
2
Building No2 – Hospitality and Staff Housing
3
Building No 3 – Classrooms and Staff Housing
4
Building No 4 – Staff Housing
6
The Clock Building – Offices, Resource Centre and the Oval Café.
7
Building No 7 – Staff Housing
8
Building No 8 – Staff and Trainee Housing, Classroom and Meeting room
9
Building No 9 – Staff and Trainee Housing
10
Building’s No 10, 11 & 12– Staff Housing
B
Bramley Building: Dining Hall and Offices
C
Chapel
F
The Factory: Gym, Crèche, Boutique, Maintenance, Grounds & Media Classroom
P
The King’s Preschool
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 21
HISTORY / PURPOSE OF ‘AT HOME DAYS’ & COMMUNITY DAYS Here is a brief overview of the vision of the ‘At Home' and ‘Community' Days’ *, from the first ‘At Home Week’ (as it was known) in 1998. We shortened them to ‘At Home Days’ in the last few years, but the heart of the purpose remains and it is the one time when everyone is present and meeting with God. It is interesting to note what Loren Cunningham spoke on the first morning: “We will come together as YWAM Harpenden community at one time and in one place to remember how God has led us and revealed Himself to us as a missionary community, to ask God to reveal to us where we are at now, and to seek Him for divine momentum and direction in the future. We intend to meet with God and one another, ready to change our course in God's direction and covenant together with Him as His people on the journey.” Some Key Aims are to: • Clarify our vision, purpose and calling in God together. • Strengthen core values through short prophetic teaching and group process. • Give a common basis for understanding a discipling, spiritually dynamic missionary community. • Agree changes in commitment and covenant before the Lord. • Spend time together around meals, in recreation and small groups. • Give and receive, promoting love and supporting relationships in the body. • Celebrate the Lord together in worship with a "prophetic edge." “It is likely to be an intense week for many of us. We don't apologise for that. Breakthroughs often come in times of urgency. That doesn't mean that we should take ourselves too seriously. We need those with the gift of humour to exercise their gifts to help us laugh at ourselves. Most of all my confidence is in God to lead us.” We all come together for this important vision and community building time, so please do not book travel or holiday time during the Community Days.... ** For the ‘At Home Days’ at the beginning of the academic year (September) we ask all staff to be on-‐site and join together to participate, so no holiday time or travel should be scheduled without permission from the Leadership Team. *‘Community Day’: we gather together as a community at different times through the year. All staff in Harpenden when the days are scheduled are expected to participate.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 22
ID (Staff Development)
We have developed a two year training programme as part of staffing at YWAM Harpenden. It is open to all new staff, but primarily aimed at the 18-‐25 year olds who have never been YWAM staff before, with the following objectives: • To journey with new staff in an increasing desire to know God, minister to Him and live lives that please Him at all times. • To help staff discover who they are in Christ and the calling upon their lives. • To prepare new staff for a variety of ministry situations, mentoring, equipping and releasing them to pioneer. • To give new staff diverse exposure to the core areas of campus life and empower and release them to take responsibility for these areas. • To facilitate ongoing and regular outreach opportunities, both locally and abroad. • To improve orientation and integration into YWAM Harpenden, England and International, and create a clearly defined track into missions ID will include orientation, character development, identifying calling and vision, project management, and training and leadership development. This will be done in the context of classroom training, but primarily through serving core areas of the campus. In addition, opportunities for further training, both within and outside of YWAM, will be encouraged.
HOLIDAYS, FURLOUGHS & TIME AWAY GUIDELINES (These are guidelines and all situations need to be discussed with team leaders) All staff are encouraged to plan time off each year, the maximum being 4 weeks (20 working days), plus the Christmas holiday* and Public/Bank Holidays** • Normally no more than three weeks of holiday are to be taken consecutively. • All time away is to be submitted and discussed with your team leader, bearing in mind that certain jobs have busy periods when time away needs to be coordinated. • Teams with a public interface should ensure coverage over summer and Christmas. • Processing Time Away: this needs to be processed with your team leaders. • We expect all staff to be on campus for Community Days in September and January. • *Christmas Holiday: Christmas leave changes according to how the dates fall. Staff will be informed of the dates in good time in order to plan their holidays. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 23
•
•
**Public and Bank Holidays: These are New Year’s Day, Good Friday, Easter Monday, Early May Bank Holiday (first Monday in May), Spring Bank Holiday (last Monday in May), August Bank Holiday (last Monday in August), Christmas Day and Boxing Day (25th/26th December). Compassionate Leave: can be taken in the event of illness, bereavement or personal crisis, and considered and worked through with your Team Leader on an individual basis. If > 3 months, it should be approved by the Leadership Team (LT).
•
Church / Christian Conferences: We take a positive view on attending conferences in may be arranged in consultation with your team leader. If you are going to represent YWAM at a conference (e.g. manning a YWAM stand) that is work; if it is to connect with your church or be refreshed, that is holiday or furlough time.
•
External Part-‐Time Study/Correspondence Courses: Any proposed course of study which is > 3 months and/or involving any of your work time must be discussed with your team leader and the LT and agreed upon before you apply to do it. Holidays, furloughs, sabbaticals and any time off must be agreed with your team leader well in advance for co-‐ordination.
•
•
Do not make travel arrangements until the dates are agreed with your team leader.
•
If you need a break because you've been working evenings and weekends, talk to your team leader.
•
When going away, inform your team leader of your whereabouts by email, so you can be contacted in case of emergency if necessary.
Maternity / Paternity Leave Our YWAM values state that: 'YWAM affirms the importance of families serving God together in missions, not just the father and/or mother. We encourage the development of strong and healthy family units, with each member sharing the call to missions and contributing their gifts in unique and complementary ways. Paternity leave for fathers is roughly ten working days unless there are extenuating circumstances, which you should agree with your team leader. Maternity leave should be discussed with your team leader & spouse. We recognise that having a baby is a major life event and takes time to adjust to. We also want to ensure that mothers do not become isolated. Furlough Furlough and holiday have different purposes. We recognise the need to visit support networks periodically to build relationships with family, friends, and church. This is furlough. For those with families abroad, it is suggested that you consider taking a maximum of 2 months furlough every two years (a guideline). YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 24
For those from the U.K, we recommend a maximum break of 6 weeks every 2 years. Consideration will be given to individual requests. Holiday allowance can be added to the furlough to extend the time by several weeks. Your Team leader should be asked to help with planning your furlough, writing letters to your church and helping you plan and set goals for your time away. Requests for furlough need to be negotiated according to course schedules and needs of the campus, and should be made with ample time for planning and communication. Furlough can be taken after a minimum length of service at Highfield Oval of 2 years. Sabbatical We recommend long-‐term staff consider a sabbatical approximately every 6 -‐ 7 yrs. Please refer to the excellent Navigators sabbatical guidelines as you plan your sabbatical proposal for leadership approval. This can be found on the Intranet at the following address: Length of sabbatical can range from 3 – 12 months. All sabbaticals > 3 months need to be approved by the LT. Before you go, remember: Leave a voicemail message on your office phone. Post an ‘Out of Office’ notification on your e-‐mail to indicate when you will return Post your away dates on the Intranet.
FAMILY LIFE YWAM Foundational Value # 15 “YWAM affirms the importance of families serving God together in missions, not just the father and/or mother. We encourage the development of strong and healthy family units, with each member sharing the call to missions and contributing their gifts in unique and complementary ways.” YWAM Harpenden welcomes families into our community. Our children are an important aspect of our community life and we hope that they will learn, grow and thrive here. The oval is a great place for children to live, play and make friends. We have many children that reside on the oval, from diverse backgrounds and a wide range of ages – here are a few pointers to help you, as parents navigate through family life here. Designated Playgrounds We have two playgrounds, designed for eight and under, as the equipment is not suitable for children over eight. The majority of the equipment in these playgrounds was donated specifically for the little ones to have a special safe play area.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 25
The responsibility for the maintenance of these playgrounds is mainly shared amongst the parents, who have been generous with their time and resources. In the past they have contributed to the upkeep of these playgrounds. These playgrounds each have a disclaimer statement, which is displayed as part of our public liability insurance. Other Areas Where Children Play As you wander around Highfield Oval, you can’t miss the many pieces of play equipment such as swings, slides, playhouses and climbing frames dotted around. The larger pieces of equipment (and outdoor furniture) usually belong to a family living in that area, but it is generally understood that they are available for all use. If you are not sure, please ask someone. When there are lots of people sharing the same things, the potential exists for us to have different experiences of community. We hope that as we all live together that the children will learn good stewardship as they learn from those around them, but sometimes we all need a little extra help (from our parents). We hope this extends to taking responsibility for fixing or replacing anything that breaks. Personal toys/ Sports equipment The Oval is a wonderful place to ride bikes and scooters, and lots of children from the local neighbourhood come here with their parents to learn! If your child (or you) has a bike, we recommend that you name it, lock it, or keep it locked away. Unfortunately we have had incidents of bike theft on the oval. Also, to avoid potential conflict or misunderstanding, please encourage your children to ask before they use another child's bike / toys as, for most of the children on the Oval these are their treasured possessions (birthday presents etc) and are viewed as private property. Safety The Oval is a most exciting place for any child to grow-‐up in. There are many hiding places, trees to climb and open space to run around and explore. It is truly a privilege to live here! We recognize that every parent has their own set of boundaries for their child, according to their age and level of maturity. Please bear in mind the following things; Not all areas of the Oval are safe for children to play – you may want to walk around with them and identify the areas that are “out of bounds”. If you are not sure yourself, you may want to check with the maintenance manager. It is also important to realise that we are not a “closed” community and have many guests, locals and general visitors each day, particularly dog walkers or those visiting the Oval Café. We encourage you to have an age appropriate discussion with your children about appropriate contact with adults and take that into account when setting your boundaries. Community Meetings Children are very welcome to our Community Meetings. Please share with them the value of worship so they can enjoy participating in worship. It is always a joy to see the children enjoying worship – especially when they’re able to join in too!! However, there are potential hazards to be aware of, such as musical instruments and electric cables, which are large and expensive to replace. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 26
If they become unsettled, feel free to take them out, there is a room (front left of the chapel) next to the toilet with baby changing facilities. Crèche We have a crèche in the factory for smaller children (0-‐3). Once a week (during term time), mums can drop off their little ones for a couple of hours to allow them to be more involved in life on the Oval. It is set up and run by mums on a rota basis. Young Adults As your child grows and increases in responsibility, it is still important that you know where they are and who they are with. Many have a mobile phone which helps, but the Oval is a public place and many other people visit the site. Young members of staff may invite your young person in for a coffee or even invite them to accompany them for a walk. We obviously work on a high trust level in the community but please be wise; invite other young people round to get to know who your young person is hanging out with and endeavour to know where they are for your and their peace of mind!!! We value different generations being linked together. Consider prayerfully if there is someone from the Oval Staff that might be willing to become a mentor and meet on a regular basis with your teen-‐age son/daughter. This can be for a limited period or open-‐ended and the breadth of discipleship/coaching should be mutually agreed. 'Wildfire' is a network within England established by King’s Kids International (KKI), YWAM’s ministry expression for children, youth and families. Oval children and families are encouraged to join in the events around the country, throughout the year and whole families are especially welcome. For more info ask at Personnel. We hope that this helps you and your family settle into life on the Oval. The best rule of thumb is, if you are not sure, just ask! The natives are quite friendly!!!
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 27
YWAM ENGLAND and Western Europe
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 28
YWAM England & Wales YWAM Harpenden is a part of YWAM England, which has more than 19 locations throughout England and Wales.
To learn more about YWAM England, visit To read the latest copy of “Advance”, the YWAM England magazine, go to
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 29
YWAM WESTERN EUROPE As we continue to grow in numbers and breadth of ministry so does our need, individually and as community, for effective networking and training. As different international events serving this need emerge, it can be a little confusing to try and identify which are for us. All of us have time and financial restraints that limit what we can participate in, so it is important that we understand the focus and intent of these different events. To help with this, the following is a brief explanation of the purpose of each of the international gatherings we currently hold in Western Europe. The Western European Leadership Consultation (WELC) The 'Western European Leadership Consultation' is held every two years. It is open to all leaders and potential leaders involved in training, evangelism and mercy ministry. The primary focus of this event is on vision, networking, pioneering, development and multiplication of the ministry in Western Europe. EQUIP 'Equip' is held every year. It is open to all staff and leaders and has a focus on equipping in skills, character and leadership principles that will benefit us wherever we are in YWAM. There is a central theme for each year, out of which flow multiple training module options, but there is always a 'classic' training track for DTS and second level school staff. Information is available at Both of these events are opportunities for us to hear from the Lord together and to engage in relationship building, networking and vision sharing. The important thing is to plan to be at the ones that are relevant to us. European Leaders Forum (ELF) A third gathering, the European Leaders Forum is a smaller gathering of regional leadership teams, major national / base leaders and family ministry leaders across the four regions of Europe: Hopefully this brings clarity and helps us plan our participation with understanding and purpose.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 30
IMPORTANT LEGAL INFORMATION AND REQUIREMENTS
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 31
REGISTERING FOR TAXES – THE BASICS Disclaimer: This document does not constitute financial advice and is subject to errors and omissions. See Appendix for detailed information regarding registering for Taxes, National Insurance and filing your tax return. We have a comprehensive document (see Appendix), which is very helpful, especially when filling out your tax assessment. All full-time volunteers with YWAM need to register with the Inland Revenue (IR) as self-employed missionaries. It really isn’t that complicated… so the sooner you start the better. Do I need to apply? For the majority of you the answer is YES! Unless you are going to be in the UK for less than 183 days within the tax year (6th April one year to 5th April the following year) and won’t extend your stay. Each year you are entitled to a personal allowance that means you can receive a certain level of income without paying tax. It may be that you do not need to pay income tax, but you MUST register with the HMRC nonetheless. You'll need to keep business records and details of your income so you can fill in an annual Self Assessment tax return. It's important to let HMRC know that you're self-‐employed as soon as possible -‐ even if you already fill in a tax return each year. If you don't tell them as soon as you begin self employment you may incur penalties. It is your responsibility as an individual to register and complete self-assessment forms. YWAM cannot do this for you. How do you register for taxes? Before you register you’ll need: • Your NATIONAL INSURANCE NUMBER (see below if you don’t have one!) • Your contact details and the contact details of your business, if you've started self-‐ employment, e.g. your home address (on the Oval) & business address • Your start date for YWAM Harpenden. • Once you have these you can register for HMRC NEWLY SELF-‐EMPLOYED via: Telephone: 0845 915 4515 (use a landline). Opening hours: Mon to Fri 08:00 to 20:00, Saturday 08:00 to 16:00; Closed Sundays / Bank Holidays. Online: • You’ll be given lots of options, but need to follow the links for one of the following: Self-‐employed and dealing with your own tax affairs Self-‐employed and wish to appoint an accountant or adviser If you have any questions, contact the HMRC helpline (number above; they are very helpful) or the Oval Personnel Department for general enquiries. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 32
The helpline is for those who are newly self-‐employed and looks at National Insurance, tax and VAT. They can also arrange for you to attend a free workshop with one of our Business Education and Support Teams to help you get started. WHEN YOU CALL THE HMRC HELPLINE, TAKE NOTE OF: • WHO YOU SPEAK TO -‐ NAME, CONTACT NUMBER? • WHEN DID YOU SPEAK TO THEM – TIME? • WHAT THEY SAY – CAN YOU GET IT IN WRITING? What is the National Insurance (NI) number? Your National Insurance (NI) number is your personal account number. It ensures that the National Insurance contributions (paid to build up your entitlement to certain benefits, including the State Pension) and taxes you pay are properly recorded on your account. It also acts as a reference number for the whole social security system. Paid contributions depend on how much you earn and whether you’re employed or self-‐employed. You stop paying National Insurance contributions when you reach State Pension age. Getting a National Insurance Number If you haven’t worked in the United Kingdom before, you need to get an NI number. • You need to arrange an ‘Evidence of Identity’ interview; call the Jobcentre Plus on 0845 600 0643 (lines are open 08:00 to 18:00 Monday to Friday.) • THERE IS NO COST FOR A NATIONAL INSURANCE NUMBER IF YOU APPLY FOR ONE THROUGH THE JOBCENTRE PLUS DIRECTLY The interview will usually be one-‐to-‐one (unless, for example, you need an interpreter). You will be asked questions about why you need a National Insurance number, your background and circumstances. You will also have to prove your identity. Bring as many 'identity documents' as possible to your interview (originals, not copies). If you don't have any of these, or other, identity documents you must still go to the interview. The information you are able to provide might be enough to prove your identity. Examples of documents which count are: • Valid passport (UK or foreign) • National identity card (UK or foreign) • Residence permit or residence card including biometric immigration residency documents • Full birth or adoption certificate • Full marriage or civil partnership certificate • Driving licence (UK or foreign) For more information on National insurance go to: • /NationalInsurance/IntroductiontoNationalInsurance/DG_190057 Income Tax when arriving in the UK YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 33
If you are a foreign national, call the Helpline (newly self-‐employed: 0845 915 4515) and they’ll help you with the process, or see the following: • TheUK/DG_078447. This page is very comprehensive with regards to all that you need to know but you may find it easier to call the helpline. If you pay tax in another country, the HMRC will guide you through the process but you still need to have documentation to prove that you have contacted them. Remember: It is your responsibility to.... • Register with HMRC • Keep accurate records • Submit a yearly tax return (if required) • Register for National Insurance.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 34
VISA INFORMATION Important Information for YWAM VISA holders When you first arrive or when you are issued with any new visa, please take all your documents (passport / visa) to the personnel office to be copied and kept in your file. Information on Renewal It is possible to renew both Tier 2 and Tier 5 visas. Tier 2 visas • Normally issued with 3 year validity, unless a shorter period is specifically asked for. • Generally renewed for 2 years, which will give the applicant a total of 5 years in the UK and allows them to then apply for Indefinite Leave to Remain (Resident visa). • Should a shorter period of validity have been originally granted (say 2 years) it may be possible to extend the validity period up to the 5 year mark when renewing. Tier 5 visas • Can only be renewed up to their maximum period of validity, which is 1 year for a Tier 5 Charity Worker and 2 years for a Tier 5 Religious Worker. • You cannot renew beyond this date under any circumstances and the holder will be required to leave the UK. Ask for advice from the Personnel Department 2 months before the time of renewal. Renewal Process Contact the Personnel Department at least 8 weeks before visa expiry to allow the system to issue you a fresh certificate of sponsorship in time for your renewal. Do not leave it too late! It is essentially the same process as for an initial application, but is simplified somewhat as the maintenance (and English requirements for Tier 2) are taken as read because of the successful initial application. • You first need to obtain a Certificate of Sponsorship Number from Personnel – there is a fee for this – see personnel for details. • After you have been issued a Certificate of Sponsorship Number, along with your supporting letter from Personnel, you can proceed with your renewal. • For more information on renewals, try the following links: Tier 5: Tier 2: lying/extending/ YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 35
Can I travel during the renewal process? The short answer is ‘No’! All renewals must be done from within the UK and no travel is permitted during the renewal process, as the applicant’s passport will be in the hands of the government during this time. • It is important that renewal is not left too late, so travel in the 4-‐6 weeks prior to renewal is to be avoided so please do NOT book travel (for teaching, ministry, outreach or sabbatical) at visa renewal time! Indefinate Leave to Remain What is Indefinite Leave to Remain? Indefinite Leave to Remain (ILR) means the applicant is able to leave and enter the UK as often as they like with no time limit on their stay in the UK. Those who are successful in being granted ILR will not have to apply for it again, and it will not expire. They will be expected to continue to work with YWAM for the foreseeable future whilst under ILR. When and how can I apply for ILR? You can apply for ILR after you have been in the UK for the qualifying period; currently, 5 continuous years with a T2 Minister of Religion / Missionary Visa. • Not all Tier 5 visas count towards the qualifying period. • Full details on applying for ILR: • In order to support an application for ILR, the personnel office is able to write a supporting letter to go with your team/centre letter endorsing their application. • Therefore, you will need to contact the personnel office for the supporting letter, with due notice, so that you can have all of the necessary supporting documentation to go with your application. • Beyond the supporting letter, the Personnel office takes no further action in ILR applications. • Please ensure that Personnel is informed of the outcome of the ILR application. If I’m granted ILR does this make me a UK Citizen? No, ILR does not confer British Citizenship. If I’m granted ILR, can I apply for a British Passport? You may not apply for a British passport unless you are a citizen of the UK. How can I apply to be a Citizen of the UK? You can apply for naturalisation (to become a citizen of the UK) if you fulfil all of the criteria listed on the following link: YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 36
PERSONAL FINANCES
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 37
MONEY, BANKS, AND SETTING UP A BANK ACCOUNT The UK currency some travel agencies. Ports, airports and larger railway stations also often have places for changing money. You will pay a charge for changing money. •
When coming to the UK, if you can, bring a small amount of sterling with you for travel, food etc. £200 should be enough to cover these immediate expenses when you arrive, or you can get cash from an ATM on arrival.
•
If you have an ATM card from another country it is advisable to inform them that you’ll be using the card in another country – be specific about where.
A Bank Account Even if you are only going to be in the UK for a few months, it is worth opening a bank account and the sooner the better. You may need proof of your home address from your home bank. Some banks do not let you open an account unless you are going to stay for at least nine months. Banks and building societies offer many types of account. •
You are most likely to need a ‘current’ account. Most current accounts remain free of charge provided you do not go ‘overdrawn’, that is, take out more money than you have in the bank. Quite large charges may then be incurred, so keep careful note of the money you put in and take out of your current account. It normally does not matter which bank you open an account with: conditions and rates are about the same.
•
If you are keeping a lot of money in the UK you should think about opening another account which will give you interest on your money. You will need a letter from Personnel to confirm that you work with YWAM, a rent bill from YWAM Harpenden and probably information (such as bills/ bank statement) confirming your address for the last three months.
Cheques and Cash cards When you open a current account you will be given a cheque book and guarantee card often called a cheque card. You can use cheques instead of cash to pay for goods and services. When you present a cheque you need to show this card to prove your identity. •
You will only be able to obtain instant credit on cheques up to the card limit – normally £50 or £100. To purchase items over this limit would normally mean presenting a cheque in advance of collection of your goods. However, be aware that some banks will be phasing out cheques. Paying-‐in books are also helpful for keeping on top of your finances.
•
You may be able to request the “Visa Debit” facility when you open your bank account. These are debit cards which you can use-‐digit code that your bank gives you) or sign the receipt.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 38
Credit Cards There are two main types, Visa and MasterCard. The different types are identical in operation. There are many shops that take these types of card in the UK. •
Items purchased on the card must be paid for on a monthly basis.
•
If you do not pay all the money outstanding on the card in one month, the balance is carried over to the next. You pay a substantial interest charge on any money carried over to the next month.
•
You may spend on each card any amount up to your credit limit. Credit cards are useful for purchasing items like concert tickets over the phone or the internet. You can also use some foreign credit cards in some bank cash machines. But be careful! It is very easy to run up large debts with credit cards.
Cash Machines Many banks and supermarkets have cash machines (or ATMs) which will enable you to withdraw money at most times. •
To use these machines you normally enter your cheque card and then type in a Personal Identification Number (PIN). The machine will then ask you what service you require.
•
You may see how much money you have in your account, order a statement or withdraw money.
•
Never keep your PIN and your cheque card together for security reasons. It is a good idea to memorise your PIN so that you don’t need to write it down.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 39
SUPPORT RAISING YWAM FOUNDATIONAL VALUE #16. Fundraising, Friend-‐raising, Support-‐raising, or whatever you call it, is part of our calling as YWAM missionaries. It is one of our foundational values as a mission and is something we all, no matter where we are from or what ministry we are involved in, do as YWAMers. Unfortunately it is often the most feared, least prioritized and most neglected part of our ministry. This is a very quick overview of the main elements needed to successfully develop a team of ministry partners. When asking people to support us financially we need to see them as partners in our ministry. They are very much a part of a team of people that make it possible for us to fulfil the vision God has given us. The best way to raise support is to approach people we already know and ask them to pray about partnering with us in ministry. Money should not be the focus; our ministry / vision should be our focus. The financial support is only a means to fulfil our ministry. Most of us struggle with “feeling like a beggar” when we ask people for money, but that’s often because we make money the focus instead of the vision God has given us. We also need to know the biblical perspective on how God provides for His people. Knowing what the Bible says in this area gives you confidence that you are following in the footsteps of good examples, even Jesus himself and Paul, of being supported by others. Jesus warns us that we can’t serve both God and mammon (the spirit that deceives us about the nature of money). It’s vital to understand the spiritual nature of dealing with money. (“Wealth, Riches and Money”, by Earl Pitts & Craig Hill, is a helpful resource) In order to be successful at fundraising we need to have a plan. Are you doing the following? • •
•
• •
Serving and building good relationships (fund raising is relationship based). Know your calling and be able to communicate it well. If you can, create a “vision statement” to put your passion for ministry into one sentence; it helps to motivate people to want to get involved and will help you keep your communication ‘vision-‐driven’ (come and join the vision) and not ‘need-‐driven’ (I need money or lack this or that). Develop a personal support plan. Make a list of people and seek God in prayer as to who to ask, make a budget so you know how much is necessary each month to live and do your ministry effectively, and create a presentation to communicate your vision in different forms such as a brochure, pamphlet or PowerPoint. Become a faithful communicator with your partners (short, often, personal) Ask people face to face – be as personal as possible. Don’t use your regular newsletter for fundraising; it should be used for telling people the stories of what God is doing and sharing the fruit of your ministry, resulting in people feeling involved. Fundraising appeals are more effective if they are separate from our regular updates and news.
Fundraising can be difficult no matter what culture you are from or what nationality, but it can be harder in nations that aren’t used to sending out missionaries. But don’t let your YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 40
culture dictate how you should do it; allow the Bible to teach you principles about inviting people to invest in your calling. The methods may look different, but the principles are the same. Read Paul’s approach to the Christians in Rome in Romans 15:20-‐24. One idea is to build a base of relationships in the nation where you work and eventually invite them to become mission partners, but this takes time. Another thing to consider is creating a “HOME FRONT TEAM” – a few people from your sending church or friends / family -‐ committed to help you. For example, one person could help with communication; another could stimulate others to pray for you; a financial advisor is also very good to have, and it may also be helpful to find an Accountability Person who will help you to follow through with the goals you set for raising support; someone to be praying with you and encouraging you (but remember they are NOT responsible for your fundraising). These are great ways for people to get involved in missions who aren’t themselves called to “go”. It is also important to look at our own lives and see if we are living lives of generosity and being good stewards of what God has already given us. It takes time and hard work to raise a team of ministry partners and to keep them, but it is well worth the effort. Not only will you be blessed, but God will also bless them and enrich their lives through being involved with you. Read Philippians 4:17. We are giving people opportunity to invest in the Kingdom – it’s between them and God how they respond. BOOKS ON FUND RAISING: ‘Funding Your Ministry’ (whether you’re gifted or not) by Scott Morton ‘Daring to Live on the Edge’ by Loren Cunningham ‘Friend-raising” by Betty Barnett ‘Funding the Family Business’ by Myles Wilson ‘The Spirituality of Fundraising” by Henri Nouwen ‘Serving as Senders’ by Neal Pirolo (for church mission committees, home front teams, etc) ‘Wealth, Riches and Money’ by Craig Hill and Earl Pitts SUPPORT-RAISING DAY Each year the ‘Support-‐Raising Team’ host days for us to gather together as a community and commit a day to training and workshops on Support Raising. These are required for all YWAM Harpenden staff, so please make sure that you listen out for the dates so that you can ensure that your diary is clear on that day. Stewardship Services also host similar workshop days throughout the year which are highly recommended.
GUIDELINES FOR STAFF FEE DEBT When a staff person is two months behind on staff fees the following will take place: • The Team Leader will be made aware (if not aware already). • The Team Leader will check if the debt can be resolved quickly. If so, they should promptly inform Personnel by e-‐mail how and when that will be done.
•
Pray together.
If not, the following steps should be taken within two weeks: • The Team Leader arranges an initial meeting between a person appointed by the Leadership Team (LT), the Team Leader, and the person in debt, to look at the reasons why they are in debt (see below for questions that could be asked). • Each situation will be different so an individual action plan will be agreed with each person. The action plan will be kept updated until the person is out of debt. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 41
•
•
The Team Leader meets with the person in debt twice a month for accountability regarding the action plan and commitment to prayer in this area. Personnel will communicate on a monthly basis with the Team Leader about who is in debt on their team and the amount.
After the initial meeting the following actions potentially could take place: •
•
•
•
•
The person in debt attends a training of some sort every quarter (e.g. 2-‐ day workshop, one morning a week for a month, etc) The person in debt attends workshops on fundraising (depending on the need of the person) If the Team Leader doesn’t feel that the person in debt can fill this role, find a fundraising coach to meet with them on a regular basis for a set amount of time (in addition to the accountability/prayer times with the team leader each month) After six months, the situation will be evaluated by a member of the LT, the Team Leader and the person in debt. If the debt has not been reduced or an inadequate increase in support has been seen, we will look at asking them to step out of full-‐ time ministry and focus on raising support to a better level before they can return. This could include leaving YWAM Harpenden and returning home but does not include stepping out of pastoral care, support from their team, or general community life if they are staying here.
Questions to consider include: • • • • • • • • • • • • • • • •
What factors do you think are contributing to you being behind on your staff fees? Do you have any other debt? How much? Do you keep accounts of all income and expenditure? Can we look at them together? How would you explain the difference between an obligation, a need and a want with some real examples? Have you acted in presumption on anything? Buying flight tickets . . . Are there ways you could reduce your living expenses? Change of housing, giving up some want? How are you communicating with your supporters, friends, family, and church? Do you have a list of relationships: friends, family, church? How do you pray for them and communicate with them? Who have you specifically asked to support you in the last six months? How did you do it? What churches are you investing in through service and relationship? How do you feel about fundraising? What are you doing to pray for finances? How do you pray? What training have you done recently in fundraising? What time are you setting aside to work on fundraising? What would you do in that time? What will you agree to do specifically and by when? Can you meet every two weeks to report on what you have done adjust the action plan and pray?
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 42
HIGHFIELD OVAL OPERATIONS
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 43
QUARTERLY COMMUNITY ROTAS All staff at YWAM Harpenden share the responsibilities of running the campus, and need to sign up for weekly work duty jobs for each quarter. This is approx 3hrs per slot / week, and 12-‐13 slots over the quarter. • This is for all staff!!! Training staff on a current school are already signed up. Other training staff need to sign up. Only one person of a married couple needs to sign up if you have children you are caring for. • Some of the jobs need one person to commit for the whole quarter. If you want to do the same job all the way through, score your name all the way through. • Find your own replacement, if you can’t be there!!! If you are going to be away please try and find someone to cover your work duty. If you are unsuccessful, get in touch with HOOT to request cover while you are away. • If you sign up for a job in the kitchen, you need to attend a Health & Safety / Bramley Hall Orientation at the beginning of the quarter. • Put it in your diary and remind yourself and each other. Check in team settings for accountability on work duties
FACILITIES BOOKING •
If you need to make an internal booking that does not involve using sleeping or eating facilities at the campus, please e-‐mail bookings@oval.com
•
If you need to make a booking for external guests, is multiple-‐days, or needs catering and sleeping facilities, then please use an Oval Booking Sheet.
•
Please note that you must submit the Facilities Request Form in advance for all events run on the Oval. Please pick up a copy from Reception, the Leadership Team Office or from the Intranet, and complete it as early as possible; ideally around four months before the event, so that we can plan our quarters more effectively.
•
You must fill in all sections of the form yourself and liaise with the various team leaders concerned, then SCAN AND E-‐MAIL to bookings@oval.com
PETS We regret that no pets are allowed in any of our staff flats, houses or bungalows. If you’d like to have pet please check with HOOT and the Housing group first.
INSURANCE Highfield Oval’s insurance policy covers only property owned by YWAM, Highfield Oval. • Personal possessions of any kind are not covered for theft, loss or damage of any kind by this policy. This applies to both staff and students. If you have valuables at the Oval, you are encouraged to arrange your own insurance coverage.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 44
RUBBISH & RECYCLING (Updated May 2011) OUR PERSPECTIVE Rubbish matters! Rubbish matters because what we do with it has a huge impact on the world around us. As Christians we should be leaders in promoting and practicing a lifestyle that tends and cares for the world God has entrusted to us. Here are three good reasons why: - We don’t know when God’s purposes for this planet will come to a close, so in the meantime we must steward it to the best of our ability. - What God put on this planet is good and worthy of being treated with dignity and respect (future generations, animals, plant life, even below-‐ground dumping sites). - Our (pretty high!) council taxes pay for these services, so we should use them as efficiently as possible, so that other good services can be provided by the council, not just loads of rubbish collection services! ST. ALBANS COUNCIL PERSPECTIVE “We share the country's concern at the impact our activities are having on the environment and the significant costs of manufacturing packaging products. We are committed to reducing our burden and offer a range of services and facilities to work toward reducing our contribution to these harmful activities.” (St. Albans Council Website) The refuse collection service is contracted to “Enterprise” from 2008 until 2015, by which time they aim to be recycling 50% of household waste. The ccontractors currently collect household refuse on a weekly basis from the 56,750 properties in the district. Normally the amount of household waste collected varies between 600-‐700 tonnes per week, but between Christmas and New Year this figure can be up to 900 tonnes. All household refuse is taken to the waste transfer station at Garston where it is transferred into bulk containers for delivery to landfill in Bedfordshire. How does the council process rubbish? All the rubbish (either from kerbside collections or waste recycling centre) collected are taken to the Councils Materials Reclamation Facility (MRF) where they are stored, sorted and baled as necessary before being loaded and sent to processors throughout the UK. Paper & magazines ⇒paper mill in Kent, Aluminium ⇒ Cheshire, Plastics & Steel ⇒ Lancashire Glass ⇒ Harlow, Essex. Cardboard ⇒Pearce Recycling in St Albans. Refrigerators and freezers are sent to specialist contractors to have their C.F.C. components removed before disposal. All re-‐useable units are renovated and sold. Hazardous waste (TVs, PC monitors, sun beds etc) and other electrical equipment are separated and collected by a specialist company.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 45
WASTE COLLECTION FROM HIGHFIELD OVAL HOUSEHOLD WASTE & RECYCLABLE COLLECTION
• Rubbish is collected on Monday mornings. Bins should be brought to the front of your building on the Oval road, by 7am on collection day. If the Monday of a particular week is a Bank Holiday or Public Holiday, the rubbish collection will usually happen on the next working day following the holiday. • One week it is BLACK bins for household (non-‐recyclable) waste and the alternate week, the GREEN bins (with a flat lid) for composting (clearer details on the next page) • Recycling bins should not be taken to the Oval road, but should be left by the side of your building. The bin men take them from the side of your building and empty them. If the bin is not very full they may not empty it as they generally only empty ones that are at least half full. • For more information on local recycling see: OTHER WASTE & RECYCLING:
• Batteries & Bulbs: Recycling boxes are in Reception to make this as straightforward as possible for all of us. • Office, class, meeting room, seminar room paper: We have several indoor paper-‐ recycling bins. They are only for paper that can be recycled, so this is clean paper. LARGER UNWANTED ITEMS / RUBBISH
• If you have large items of furniture, fridges, washing machines, old furniture, car batteries, or junk, please note that it is your responsibility to dispose of these correctly. • For example, large electrical items and old furniture should be taken to the local bulky Household Waste Recycling Centre which is in Dark Lane, off Grove Road, in Southdown, AL5 1QB. For directions, ask Personnel or a neighbour. • Please do not assume that someone else will want what you are throwing out. • Advertise the item for a week or two on the Intranet and then if there are no takers, please take it to the dump. • DO NOT STORE ANYTHING IN THE FACTORY WITHOUT PERMISSION FROM H.O.O.T.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 46
WHAT IS COLLECTED VIA YOUR HOUSEHOLD KERBSIDE COLLECTION If anything is TOO BIG to fit in these bins please take them to the bulky waste recycling centre HOUSEHOLD WASTE COMPOSTABLE WASTE Please note all refuse must be inside Please note all garden waste, your black wheeled bin, we will not cardboard and food waste must take excess waste. be inside your green wheeled bin/bag/caddy, they will not take excess waste. Wrap all your food waste in newspaper to prevent maggots & flies. We want We don’t want X We want We don’t want X Everything which Paint Animal bedding Ash cannot be recycled or Rubble i.e. brick, Bark Coal reused concrete, wood Card, Cardboard Flower pots Recyclable items Cereal Boxes Plant trays Compostable items Coffee grounds Plant wrappings Cut flowers Plastic carrier bags Eggs & Egg boxes Rubble PAPER BOX Fish, Meat & Poultry -‐ Refuse sacks cooked and uncooked Soil including bones Stones Fruit & Vegetable Tetrapacks – paper peelings based liquid food and Grass & Hedge drink cartons We want We don’t want X cuttings Yellow pages catalogues card Hay, straw, leaves & junk mail cardboard Paper compostable bin weeds magazines & envelopes liners -‐ £1 discount on most Shredded paper newspapers shredded paper products available to St Small branches & telephone directories Albans City & District twigs residents at yellow pages Use Tea bags PLASTIC & CANS BOX Please squash cans, if possible. Please empty aerosols but do not puncture or crush. Plastic coloured bottles that have contained household cleaners, washing up liquid, bleach, shampoo and fizzy drinks are all acceptable. Household aerosols including air freshener, deodorants, hairsprays, cleaning products, insecticides and shaving foam are all acceptable. We want We don’t want X Aluminium foil engine oil containers Aerosols film Cans -‐ food and pet ice cream tubs food margarine tubs Drinks cans meat/microwave trays Plastic BOTTLES plastic wrap punnets yoghurt pots
voucher no. 48234 when ordering.
GLASS BOX Please remove corks (and place in your refuse) and give all items a quick rinse but you don’t have to worry about removing labels.
We want Glass bottles Glass jars
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 47
We don’t want X broken glass drinking glasses light bulbs mirrors plate glass Pyrex or similar (this is heat treated and cannot be recycled) spectacles
MAINTENANCE & GROUNDS HOUSE DÉCOR If you want to redecorate your room or flat, this can be done at your own expense. If the room does not need decorating but you would just prefer another colour scheme, it is your personal responsibility but please use a neutral colour. The Oval will supply magnolia or white colours for walls and white for the woodwork where it is used. The Oval will also supply rollers and brushes etc. • Spillages and damages while painting should be rectified by the staff member. • Furniture must not be removed from any room or flat without permission. Check with Personnel if you are in doubt. • Ordinary decorating should be done in your own time. The maintenance department must be consulted before any structural work is undertaken, and they can only assist with structural and skilled work as it fits into their schedule. • If an emergency has caused your housing to be unsuitable to live in and you have the skills to deal with it, time can be taken out of the week to do it after discussion with your Department Head and the Personnel Department, as long as this does not hinder your main work being completed. DAMAGED PROPERTY Please encourage one another to be good stewards of The Oval’s equipment and property. If damage occurs as a result of misuse or abuse, it is expected that replacement or repair of the property is processed with the Department Head concerned. We encourage that as much as possible of the cost is covered by the person who damaged it. MAINTENANCE REQUESTS Work request forms are available from Reception for small maintenance tasks around the Oval (dripping taps, broken handles, blocked drains etc). If you are DIY competent, please feel free to fix it yourself. If not, please ask your building / flat coordinator about it, and if that person cannot do the repair, they will complete a form and put it in the ‘Maintenance’ post box, rather than reporting it verbally. Alternatively you can e-‐mail your request to: maintenance@oval.com WORKSHOP We try to make the workshop available to all; however any use of the workshop requires permission from a maintenance staff member and appropriate training if necessary. You may e-‐mail to maintenance@oval.com for this request. You need to be instructed as to what you may use safely. Whatever you do must be cleaned up immediately. • Assume that anything cannot be used until you ask if it is okay. The Maintenance Team notice straight away if something is out of place, and if a tool is not where it should be it can delay anyone trying to do a task. Seldom do we find the workshop tools etc as we expect them to be, and this can be awkward. • Keys for the workshop are available at reception where they need to be signed for. • If anyone hears running water on the site late at night or in a place that may seem odd, please let HOOT know as soon as possible YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 48
ENERGY Be aware of buildings using too much heating when the weather is warmer – it still costs us. • On cold days, please don’t leave windows or doors open. • Be sure outside doors are actually closed; they don’t all have spring closers and tend to stick more in winter because the doors swell in the damp weather. • Please remember to turn off unnecessary lighting in entrances or hallways. GROUNDS The grounds are maintained by everyone on the Oval. Some tools are available in the grounds shed, your house may have privately owned or Oval tools, and some restricted tools like strimmers / weed-‐whackers and hedge trimmers are stored at house No.1. • You should use them only once the grounds staff has shown you how to use them and how to deal with the trimmings. • All tools must be returned immediately in case someone else is waiting for them. • Please wear safety equipment, which is either with the machines or in the grounds shed. There are some diesel, some petrol and some petrol / oil mix machines, so ask grounds staff until you are familiar with the machinery. • Tractors are only driven by those registered on our insurance policy and trained by the grounds staff. Normally a UK driver’s licence and an age limit applies. • The key for the grounds shed is kept in reception where it needs to be signed for. BLOCKED DRAINS In the past we have had to pay a significant amount of money on clearing the main drain behind 7, 8 and 9, as it was blocked all the way up to the road. This is partly due to the drain connections being of insufficient width as the original plumbing is old, but the problem is made worse by things being put down the drain that should not. Please take time to read the following instructions. Many of you will know this, but as we all come from different places, with different plumbing systems, it may not be obvious to all. The only things that should go down your toilet are toilet paper and human waste. All that should go down your sink is waste water. Things to not put down the drain of your sink or your toilet: • Grease; this includes fat from cooking – bacon, sausages, or any other meat in particular. Grease should be tipped into a container (an old tin can works well, or, wait until the grease solidifies and scrape it into a plastic tub) and disposed of in the bin. This also includes butter or any fat which will go solid when cold. • Sanitary napkins of any size, tampons, nappies. All must be disposed of in the bin. • Condoms or other contraceptive devices. • Please make every effort to help us avoid spending more money on clearing drains. • Please make sure this is clear to guests and trainees. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 49
LAUNDRY Laundry facilities, with washing machines and dryers, are available in each building and there are also clothes lines in the back gardens for drying clothes. There is a small cost for use of the washing machines; please see instructions in each building for which coins you need. You need tokens for dryers (50p from designated flat coordinators) for 20 minutes.
SECURITY We do have a crime problem in this area of Harpenden, and your participation helps make the Oval safer for all of us. • Coded keypads or card readers have been installed on most outside doors and there are alarms in the Clock Building, Bramley Building, Bramley Hall, Maintenance, and the Factory. • A crucial aspect of our security lies in keeping these codes confidential amongst only those who live and work at the Oval. • ALL COMMUNAL DOORS in the residential buildings should be locked at all times. Doors to the Clock Building and Bramley Offices should be locked outside office hrs.
•
The electric gate on the main entrance is automatically locked from 20:30 until 07:00. The old wooden gate at the front of the Oval is shut around 22:00. Please close the gate after you if you open it before 07:00.
SECURITY ROTA The men who live on the Oval take it in turns to do a security check of the Oval each night throughout the year. This service is vitally important, as evidenced by the number of unlocked doors and open windows found most nights. • Each man needs to sign up for TWO WEEKS a year so that this can easily be covered. • Unless you are not physically able, please sign up (this counts as one of your 3hrs per week work duty slots) • You can sign up on the Intranet. Go to “Security Check Rota” and click on the date you want, then “edit item” to add your name. • If you need to change the week you are on, please change the rota when you swap with someone. Please look in the appendix for the security rota, door codes and the code for the electric gate. TRESPASSING and UNACCEPTABLE BEHAVIOUR There has been some confusion regarding trespassing on the Oval; who is allowed to be here? What are they allowed to do? What should we do if we see unacceptable behaviour? It will be most beneficial if we are consistent in our approach to visitors both welcome and unwelcome. Here are some guidelines to help you know how to approach both: STRANGERS Feel free to approach strangers and ask, “Can I help you?”, “Have you come to visit our Café?”, or “How long have you been part of the Dog Walking Scheme?” Assume the best by asking open questions. This applies particularly to people who look lost or are in non-‐public areas, such as around the buildings or anywhere other than the Oval road or back fields. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 50
•
•
Be polite but be aware -‐ if someone is here innocently, they will not be offended if you ask what they are doing. If someone gets aggressive, you can ask them to leave the property, or find someone else if you don't feel comfortable doing that, such as an LT member.
CHILDREN Children and young people should not be on the Oval unaccompanied unless at the express invitation of a resident. This means that children cannot play here anytime just because they know somebody who lives here – they must be invited by and with the person they know. • If a child tells you that they know a resident, ask them where their friend is, and if they are not here by invitation at that time, please ask them to leave. • This is for their safety and for our protection as a community. YOUNG ADULTS AND THE SPORTS FIELD Unless here specifically to visit a resident or for a public event, young people are not allowed to “hang out” on the Oval -‐ for their safety and for our protection as a community. We are happy for young people to play sports on the back field provided they do not follow the game with drinking alcohol and littering, and they must abide by our opening hours. • If you see young people playing at the back field, please approach to make sure they are doing only that, and ask them to leave if they are not. • In the past there have been incidents of vandalism mainly of the cricket pavilion. This is not acceptable. If you observe this behaviour and don't feel comfortable approaching them yourself to ask them to leave, please ask someone else to do so. • We have been encouraged by the police to take photographs of such behaviour, in case we are forced to prosecute. DANGEROUS DRIVING We have also had repeated incidents of dangerous driving on the Oval. • Please take the license plate number of any vehicle causing a disturbance and give it to a member of the LT or HOOT along with a description of the activity, as we can report this to the police who will issue warnings and prosecute repeat offenders. LOST PROPERTY There is a lost property box in Reception. Please put items you find there. If you aren’t able to find something and it isn’t in the lost property box, put a notice on the Intranet. If you have any questions about security on the Oval, please email them to HOOT at hoot@oval.com. If we all cooperate, we can help make the Oval a safe and pleasant place for everyone who lives and visits here.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 51
HOSPITALITY YWAM Foundational Value .”
We as a community believe that hospitality is the privilege of the whole community to make people feel at home, welcomed and truly wanted. The meaning of hospitality is “friendly and kind behaviour towards guests or strangers”. It isn’t just about a bed for the night, it’s about helping people know that they are welcome, even if it’s just with a cup of cold water. We love to meet new people, such as at Community Meeting or at meal times. • When you as a staff member have a personal guest to stay, they can either stay in a guest room in one of the accommodation buildings or in the Hospitality House. THE HOSPITALITY HOUSE We are blessed to have a house at YWAM Harpenden which is dedicated to receiving visitors connected to YWAM Harpenden in some way. These visitors are personal guests, speakers on our training courses, visiting YWAMers or family of staff. In most cases there is a small cost for Bed & Breakfast which the team will explain when you book. Please book early to avoid disappointment. THE OASIS One part of the Hospitality House is set aside for visiting YWAMers who have recently been through a challenging time, or are in need of refreshment or debriefing. This flat is called the Oasis, and is suitable for families as well as singles. • For enquiries, please contact hospitality@oval.com GUEST ROOMS IN INDIVIDUAL BUILDINGS Most buildings have their own guest room, with guidelines for visitors decided by the house. Procedures for the use of these can be found from house / flat co-‐ordinators, including the details of cost (if any). If these rooms are full, you can put an announcement on the Intranet to see if your friends can stay in a friend’s home, and in the last instance you may want to contact the building No.9 co-‐ordinator to see if there is a room available. GLEANINGS In Ruth 2, Boaz instructs his farm workers this way: “Even if she (Ruth) gathers among the sheaves, don’t embarrass her. Rather, pull out some stalks for her from the bundles and leave them for her to pick up, and don’t rebuke her.” Some amongst us are at times, like Ruth, in need of food. The “Gleanings” cupboard was established a few years ago to try to meet this need. The cupboard is at the rear of Hospitality above a small freezer (also for Gleanings) and is supervised by Hospitality Staff. Who can benefit from the Gleanings? • If you would like to take from the Gleanings, please speak to the Hospitality House, who keep a list. This list is reviewed from time to time with the LT. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 52
WHAT DOES GOD’S WORD SAYS ABOUT HOSPITALITY? Let us outdo one another in serving. The Jesus in you and me should be anxious to serve. 1 Peter 4:9-‐10: Cheerfully share your home with those who need a meal or a place to stay. God has given each of you a gift from his great variety of spiritual gifts. Use them well to serve one another. (NLT) Hebrews 13:2: Do not forget to be kind to strangers for some who have done this have entertained angels without realizing it. Isaiah 58:7-‐9: I want you to share your food with the hungry and bring right into your own homes, those who are helpless, poor, destitute. Clothe those who are cold and do not hide from relatives who need your help. If you do these things, God will shed His own glorious light upon you. He will heal you; your godliness will lead your forward; and goodness will be a shield before you, and the glory of the Lord will protect you from behind. Then you will call, the Lord will answer, “Yes, I am here.” He will quickly reply. All you need to do is stop making false accusations, spreading vicious rumours. Acts 2:44-‐46: And all the believers met together constantly and shared everything with each other, selling their possessions and dividing with those in need. They worshipped together regularly at the Temple each day, met in small groups in homes for Communion, and shared their meals with great joy and thankfulness. Hebrews 6:10: For God is not unfair. How can He forget your hard work for Him, or forget the way you used to show your love for Him – and still do by helping His children? Proverbs 3:27: Do not withhold good from those to whom it is due, when it is your power to do it. Proverbs 11.25: A generous man will prosper; he who refreshes others will himself be refreshed. Romans 15:32…so that I may come to you in joy by the will of God and find refreshing rest in your company. Matthew 25:37-‐40: Then the righteous will answer Him saying, “Lord, when did we see You hungry, and feed You, or thirsty, and give you drink? And when did we see You a stranger and invite You in, or naked, and clothe You?” And the King will answer and say to them, “Truly I say to you, to the extent that you did it to me of the least of these brothers of Mine, you did it to me.”
Colossians 4:5: Conduct yourselves with wisdom toward outsiders, making the most of the opportunity. Mark 10:43-‐45: But among you it will be different. Whoever wants to be a leader among you must be your servant, and whoever wants to be first among you must be the slave of everyone else. For even the Son of Man came not be served but to serve others and to give his life as a ransom for many. Hebrews 10:24: Let us think of ways to motivate one another to acts of love and good works. Philippians 2:3-‐4: Don’t be selfish; don’t try to impress others. Be humble, thinking of others as better than yourselves. Don’t look out only for your own interests, but take an interest in others, too. Galatians 6:9-‐10: And let us not get tired of doing what is right, for after awhile, we will reap a harvest of blessing if we do not get discouraged and give up. That is why whenever we can, we should always be kind to everyone, and especially to our Christian brothers. Romans 12:13: When God’s children are in need, you be the one to help them out. And get into the habit of inviting guests home for dinner or, if they need lodging for the night. 1 Timothy 3:2: An overseer, then, must be above reproach, the husband of one wife, temperate, prudent, respectable, hospitable, able to teach. Mark 9.41: For whoever gives you a cup of water to drink because of your name as followers of Christ, truly I say to you, he shall not lose his reward. Romans 12:10,16,20: Be devoted to one another in brotherly love; give preference to one another in honour: Be of the same mind toward one another; do not be haughty in mind, but associate with the lowly. Do not be wise in your own estimation. But if your enemy is hungry, feed him, and if he is thirsty, give him a drink; for in so doing you will heap burning coals upon his head. Luke: 14:12-‐13… When you put on a dinner, He said, “Do not invite friends, brothers, relatives, and rich neighbours! For they will return the invitation. Instead, invite the poor,
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 53
the crippled, the lame and the blind. Then at the resurrection of the godly, God will reward you for inviting those who cannot repay you.” John 13:14-‐16: hi
Love One-Another Love 1. Love one another (Jn 14:34; Jn 15:12, 17; Rom 13:8; 1 Pet 1:22; 1 Jn 3:11; 1 Jn 4:8) 2. Be devoted to one another (Romans 12:10) 3. Have concern for each other (1 Corinthians 12:25) 4. Be kind to one another (Ephesians 4:32; 1 Thessalonians 5:15) 5. Bear with one another (Colossians 3:13; Ephesians 4:2) 6. Forgive one another (Ephesians 4:32; Colossians 3:13) 7. Comfort one another (1 Thessalonians 4:18) 8. Be hospitable to one another (1 Peter 4:9) 9. Serve one another (Galatians 5:13) 10. Carry each other’s burdens (Galatians 6:2) 11. Pray for one another (James 5:16) 12. Be compassionate to one another (Ephesians 4:32) 13. Greet one another with a kiss (1 Corinthians 16:20; 1 Peter 5:14) 14. Do not wrong one another (Leviticus 25:14) 15. Do not deprive one another (1 Corinthians 7:5) Trust 16. Submit to one another (Ephesians 5:21) 17. Confess your sins to one another (James 5:16 18. Speak the truth to one another (Zechariah 8:16) 19. Live in harmony with one another (Romans 12:16) 20. Do not lie to one another (Colossians 3:19) 21. Do not slander one another (James 4:11) 22. Do not grumble against one another (James 5:9) 23. Do not go to law against one another (1 Corinthians 6:6) 24. Do not provoke and envy one another (Galatians 5:26) Respect or honour 25. Accept one another (Romans 15:7) 26. Encourage one another (1 Thessalonians 5:11; Hebrews 3:13; Hebrews 10:25 27. Build one another up (Romans 14:19; 1 Thessalonians 5:11) 28. Belong to one another (Romans 12:5) 29. Honour one another (Romans 12:10) 30. Wash one another’s feet (John 13:14) 31. Consider one another better than yourself (Philippians 2:3) 32. Be humble towards one another (1 Peter 5:5) 33. Spur one another on (Hebrews 10:24) Understanding or knowledge 34. Have fellowship with one another (1 John 1:7) 35. Be at peace with one another (Mark 9:50) 36. Teach one another (Colossians 3:16; Romans 15:14) 37. Admonish one another (Colossians 3:16) 38. Speak to one another (Ephesians 5:19) YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 54
FIRE SAFETY WHAT TO DO IF YOU DISCOVER A LARGE FIRE • Do not attempt to extinguish any fire unless it is safe to do so…. • Leave the property • Close all doors behind you • Do NOT go back into a burning building for anything
* THE GATHERING PLACE IN CASE OF A FIRE IS THE MIDDLE OF THE OVAL • •
Dial 999 If there is still someone inside the building, tell the Fire and Rescue Service when they arrive -‐ they will be able to find the person quicker and more safely than you
•
Do not go back until you are told it is safe to do so by the Fire and Rescue Service
GETTING HELP - DIALLING 999 / 112
•
Dial 999 Your call will be answered by an operator who will ask you which emergency service you require and the telephone number that you are dialing from You must stay on the line and you will then be connected to the Fire and Rescue Control Room in the area you are calling from, not the local fire station As you are connected to the Fire and Rescue Service you will hear the telephone exchange operator pass your telephone number to the fire brigade control operator. The Control Operator will ask you some questions….
-
What is on fire? What is the address? What is the nearest main road? What town are you in? Don’t put the telephone down until they have taken all the details!
•
If you are trapped and unable to leave, the operator will stay on the phone line with you and give you fire survival guidance to help you until the fire engine arrives MAKE SURE THAT IF YOU CALL THE EMERGENCY SERVICES BETWEEN 22:00 & 07:30 THAT YOU SEND SOMEBODY TO OPEN THE ELECTRONIC GATE TO ALLOW THE EMERGENCY SERVICES TO ENTER THE PROPERTY
• • • •
•
WHAT TO DO IF YOU DISCOVER A SMALL FIRE: • Do not attempt to extinguish any fire unless it is safe to do so…. • There are two types of fire extinguisher suitable for use on the Oval (see below) • Please report to HOOT if they are not there or have been used so it can be replaced • Take note of fire exits and location of extinguishers • NEVER prop open a fire door – there’s a £5000 fine for propping open a fire door and an extra £5000 if you do it with a fire extinguisher YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 55
Water Spray Extinguisher Fires involving organic solid materials such as wood, cloth, paper, plastics, Coal etc. Danger : Do not use on burning fat or oil or on electrical appliances How to Use Point the jet at the base of the flames and keep it moving across the area of the fire. Ensure that all areas of the fire are out. How it Works Water has a great effect on cooling the fuel surfaces and thereby reducing the pyrolysis rate of the fuel. Instead of a jet nozzle a spray nozzle is used, with a higher pressure, which creates a fine spray. This allows for a given quantity of water to have a considerable increase in the surface area presented to the fire. This makes extinguishing more efficient by more rapid extraction of heat, formation of steam etc.
Carbon Di-Oxide Extinguisher Best For ELECTRICAL & FLAMMABLE such as grease, fats, oil paint, petrol etc but NOT KITCHEN FRYING PANS Danger:. How to Use The discharge horn should be directed at the base of the flames and the jet kept moving across the area of the fire. How it Works Carbon dioxide extinguisher works on classes B and C and works by suffocating the fire. Carbon dioxide will not burn and displaces air. Fire Blanket Fire blankets are made of fire resistant materials. They are particularly useful for smothering flammable liquid fires or for wrapping round a person whose clothing is on fire. There should be a fire blanket in every kitchen. Best For Fires involving both solids and liquids. Particularly good for small fires in clothing and for cooking oil / frying pan fires provided the blanket completely covers the fire.
Danger: If the blanket does not completely cover the fire, it will not be able to extinguish the fire. How to Use Place carefully over the fire. Keep your hands shielded from the fire. Do not waft the fire towards you. How it Works Smothers the fire and prevent oxygen getting to the fire.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 56
FIRE PREVENTION Smoke alarms are devices that incorporate a means of detecting a fire (smoke detector) and giving a warning (alarm). They are about the size of a hand and are normally fitted to the ceiling. They can detect fires in their early stages and give you precious minutes to enable you and your family to leave your house in safety. • We recommend that you purchase a smoke alarm and regularly check it. They cost very little to purchase. They are very sensitive to small particles of smoke produced by flaming fires, such as chip pans, and will detect this type of fire before the smoke gets too thick. They are marginally less sensitive to slow burning and smoldering fires which give off larger quantities of smoke before flaming occurs. FIRE EXITS & FIRE DOORS • Do not block exits or leave furniture in hallways that could be a hazard if there was a fire. There are clearly marked FIRE DOORS in all the buildings. These doors need to remain shut at all times as they are specifically designed to prevent fire spreading. • The buildings on the Oval are all old and are in a conservation area, so have lots of old wood (floors, windows, beams etc). • Please be aware that candles are not allowed in building No.9 and in other areas should not be left unattended. • Smoking is not permitted in any of the buildings at YWAM Harpenden.
RECEPTION Reception is open Monday to Friday from 09:00 -‐ 13:00 and 14:00 -‐ 17:00; after office hours, an emergency-‐only phone number is available on the recorded message. • We do not have a full-‐time receptionist, so this is one of the available weekly work duty jobs for all staff. Please speak to Personnel and we will get you trained! • Reception is the place to look for the fax machine, the franking machine, office supply catalogues, telephone directories and the lost property box. POST / MAIL Post is delivered daily, except on Sunday. After sorting, it is put into mailboxes (commonly referred to as pigeon-‐holes) in the Clock Building. A specific staff member will sort the mail into the pigeon-‐holes during the week. • If goods are being delivered that require a signature, please try to locate the person responsible for ordering them so that they can be checked and signed for, and any delivery receipts should be placed in the Accounts Mail slot. • For outgoing personal mail: place stamped mail in the tray marked ‘Stamped Mail Tray’; this is collected around 15:00 Monday – Friday. Lists of postage rates and scales for weighing letters are in Reception. There is also a Post Box by the front gate. This is collected twice daily and on Saturdays. It is for stamped letters only. • For outgoing business mail: There is a franking machine in Reception for business mail. Please use the correct code (list on franking machine) for your department, then put into the correct mail bag, i.e. 2nd class, 1st class, international. For special delivery and parcels, please follow the directions posted in reception. If in doubt, please check with the operations administrator. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 57
STAMPS & STATIONERY • Stamps may be purchased at the Post Office and some other shops in Harpenden. • Office supplies can be ordered via reception for your office. Please use the forms provided in Reception or the Bramley Building. • Please note that YWAM letterhead is NOT for personal use, including newsletters and the YWAM logo is not to be used on personal letters / newsletters. • Speak to YWAM Harpenden Communications if you would like clarification on this.
TELEPHONES THE TELEPHONE SYSTEM AT YWAM HARPENDEN • To make an outside call: dial 9, then your three digit personal code, then **, and finally the telephone number you require. You do not have to pause at any stage. • You should already have been given your personal phone code, but if not, please see the Personnel Department to have one allocated to you. For work purposes, your department leader will provide any necessary work codes. • Please note that personal phone codes are only available for staff; students have to use the payphone for making personal calls. • You may print out your own copy of the telephone list from the Intranet. • For instructions on how to answer and transfer calls from Reception, please refer to the Reception Manual (in Reception). • Do not give out any mobile or home phone numbers without express permission – this is especially important if you are working on Reception. Take a message instead. YWAM HARPENDEN PHONE BILLS Details of all outgoing calls made with personal codes are logged by our telephone system. These are used to produce phone bills; the amount included on your invoice from Accounts. TIPS ON HOW TO AVOID EXPENSIVE PHONE CALLS • The peak rate for phone calls is 08:00 to 18:00 Monday to Friday. Outside these hours, calls can be much cheaper. For mobile phones, the evening rate usually starts later (e.g. 19:00). With phone-‐cards, the rate is usually the same at all times. • All local and national calls are significantly cheaper at the weekend. So if you want a long chat, try waiting until Saturday or Sunday (at any time of the day). INTERNATIONAL CALLS If you will be on staff long-‐term and want to make international calls regularly, it may be cheaper to get an account with an international phone company. Speak to somebody from your country or continent for advice. • To call another country from the UK, dial 00 before the country code. You can make international calls from most phones, including public phones, by dialling the number directly. However, it is usually cheaper to use, Skype on your computer, a phone-‐card or to use an international calling company. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 58
PUBLIC TELEPHONES / PAYPHONES There are public telephones in many places. Some of them also have Internet access. You will usually find illustrations and instructions on how to use the phone and you can pay for calls with coins, a phone card or a credit card. To use a public telephone: • Most public phones are provided by British Telecom (BT), but you sometimes see payphones provided by another company. You may also find payphones in buildings such as hotels, which are run by the building’s owner who may set higher charges. • If using coins: lift the handset and insert money (at least 20p for local calls). Enter the number. When your money has almost been used up, you will hear some beeps prompting you to add more coins or to finish your call. • If you are using a credit card: lift the handset and then swipe the card through the slot. You can then dial the number you want. It is often more expensive to pay by credit card. If you are using a phone-‐card: see below. PHONE CARDS • Pre-‐payment phone cards are usually the cheapest way of making an international call, and can also be used for calls within the UK. • You can buy phone cards from newsagents, post offices and other shops. Many companies offer these cards, so it is good to compare prices when buying one. • To make a call using a phone card, dial the 0800 or 0808 number on the back of the card to be connected to the phone card company. Next enter the PIN number on the back of your phone card. Then dial the number you want. FINDING NUMBERS • You can find numbers of local residents and businesses in the telephone directory. In the front of the directory you will find the dialling codes for many countries and cities in the world. You can also find contact details for local companies (listed by subject) in the Yellow Pages books, and from their on-‐line directory • You can also call a Directory Enquiries services to ask for any telephone number – although there is a charge for all of these services. Several companies offer a Directory Enquiries service, with different prices, but all the numbers start 118. The person you speak to will offer to connect you to the number they give you -‐-‐line. This has a link to some international directory enquiry Websites.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 59
DIRECT DIALLING AND THE OPERATOR You can usually make telephone calls by keying the number directly into most telephones in the UK. However, it is occasionally difficult to get a connection or you may need to ask a question about using the telephone. In this case, phone either the UK operator (100) or the international operator (155) to be connected. Both operators are free but if an operator connects you, the call is charged at a much higher rate than if you dial the number yourself. MOBILE PHONES Mobile phones in the UK use GSM standards, so if you already have a GSM phone, you can often just buy a new SIM card and continue to use your phone. The main mobile networks at the time of writing are: T-‐Mobile, Virgin, Orange, Vodafone, O2 and 3. Each of these companies offers various packages and tariffs. • Start by visiting a shop that sells mobile services for all networks. Get advice from the shop assistant on the most economical package for the amount of time you plan to use your mobile phone – for example, pay-‐as-‐you-‐go packages are more economical if you do not use a mobile phone very often. If you send a lot of text messages, look for a package that makes each text message more economical. • It is often very expensive to call mobile phones on a different network – so be careful when you call other mobile numbers! Investigate all the options before signing up. • Remember, calls from landline phones to mobile phones are more expensive than calls to other phones, so people who call you may not want to talk for too long! COMPUTERS, INTERNET & EMAIL • YWAM Harpenden is fortunate to have a secure network that gives us unlimited broadband access to the Internet. Our IT department provides secure services for our own base as well as for workers in sensitive locations around the world. • To connect to the network we require that you have anti-‐virus software installed. For ministry computers we use Sophos antivirus. For personal computers you can use the antivirus software of your choice, but Sophos is recommended. We have both wired and wireless access in all the Oval buildings. • You will need a member of the Network team to load your computer or wireless device onto the network as your IP address needs to be loaded onto our system. You will receive your YWAM Harpenden e-‐mail address, phone use code and Intranet logon, which the Network Team will explain to you. • The cost to access the network is approximately £10 per month per access site. This includes your e-‐mail address, unlimited Internet access, antivirus protection and the continued development of the network. A hardware firewall protects our network and provides network filtering to protect from unwanted or inappropriate content. • We discourage the use of P2P File sharing programs. Sometimes they are used for a single file, but even one file can cripple the network, which is why we block them with our firewall. If someone tries to use one, the most likely result will be they find it doesn’t work-‐ or at least not work very well, because the firewall is knocking it off. • The Network Team is glad to provide personal assistance with your computer problems when we have sufficient personnel. However, in the absence of a full team, YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 60
personal assistance will be limited to issues related to the network only. YWAM HARPENDEN INTRANET An Intranet is like a Website, but only people who are signed on to it can access it. YWAM Harpenden Intranet is the place for news and opinions relevant to life on the Oval and holds a wealth of information, documents, contacts, fun and photos. • Everyone should regularly log-‐on to keep up to date on essential happenings, and also be your first stop for bookings forms, phone numbers and other information related to base life. • You are invited to post things on the Intranet that will be of help to the rest of the community. It is best to browse and see what’s there. It’s really easy – we promise! To get to the Intranet type: type or in your web browser. You will be asked for your oval email address & password. Then click and go! YOU MUST NEVER SHARE YOUR NETWORK PASSWORD WITH OTHERS.
FACILITIES on the Oval In addition to the rooms and buildings that are bookable (via HOOT), there are also other facilities available on the Oval for YWAM Harpenden Staff. OUTDOOR & SPORTS EQUIPMENT In most cases, the majority of sports & outdoor is under the ownership or stewardship of an individual or team. This includes the BBQ’s, football & volleyball equipment. • Please check with HOOT, Forever or Oval Sports United if you have any questions. FITNESS on the Oval Behind the Factory there is a small but well-‐equipped room with some good cardio-‐vascular exercise machines, a 3-‐station weight training multi-‐gym and an extensive array of free weights equipment. It is accessed through the crèche room. • For reasons of health and safety and insurance we require all users to go through an induction to the gym and to sign a release form before you begin training. • Much of the equipment was purchased by members of staff for the benefit of all, so please feel free to make a donation towards the upkeep and purchase of new equipment in the future and please do take a turn to dust, polish and vacuum the room from time to time. We need a volunteer to clean once a week. • Please do not allow children to be in the gym unaccompanied. • Please also ensure you have taken medical advice, before embarking on vigorous physical training, especially after a long period of relative inactivity. • There are group fitness sessions available to all staff and trainees of YWAM Harpenden, at 06:30 – 07:15 Mon, Wed, & Fri, facilitated by YWAM Harpenden staff. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 61
BLESSINGS BOUTIQUE God has good gifts for his children. We hope that the Blessings Boutique will live up to its name and bless those who give and receive used clothing and miscellaneous items from it, but we all need to be good stewards of the Boutique. • If you find donations that are in a bad condition, please put them in the recycling bin. • When choosing goods to take to the Boutique, please remember the following principles: - All items must be clean, washed and not damaged (e.g. for CLOTHES: does the zip work? Do the shoes have laces?) - NO UNDERWEAR - No books* *If you have good quality Christian books or novels, please speak to the training department to see if they would like them. - No furniture or electrical items ** Please put a note on the HAVE GOT NEED section of the Intranet. • Please do not give the Boutique code to people who do not live here. • If you want to bless a visitor with clothes from the Boutique, please take them into the Boutique and stay with them while they choose something. • An adult must accompany children under 16 visiting the Boutique.
FACILITIES OPEN TO THE PUBLIC The Oval is used by many groups during the week. For example, Harpenden Colts Football Club play and train on the back field on Sundays during the football season and pupils from The Kings School in Ambrose Lane regularly play sport on the netball pitch and back field. • Members of the public are permitted to use the backfields for football and other games, but we do not wish to have the Oval used as a public park. • Visitors are a deterrent to vandalism or criminal activity in the secluded areas of our property; however if you see anyone acting inappropriately on the property you may approach them, or ask one of the LT to do so, or call the police if appropriate. OVAL CAFÉ The Oval Café opened in 2007 as a ministry to bless the local community, serving the best quality, ethically traded teas and coffees, hot and cold drinks, home baked goods and Panini’s. It is an extension of our heart of welcome and hospitality, with free Wi-‐Fi for our visitors. • The Oval Café is open Mon – Fri, 09:00 – 17:00, and Sat, 11:00 -‐ 16:00. • To book the Oval Café for an event, please obtain a booking form from café manager • The café offers a 25% discount on pre-‐paid cards for YWAM Harpenden staff and is a key place for us to extend Jesus’ model of hospitality.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 62
DOG WALKERS SCHEME There are a group of people who live locally, wear wellies, and like to walk in the woods in the company of furry, four-‐legged creatures. We affectionately refer to them collectively as “the dog-‐walkers”. • People can apply annually for a permit allowing them to walk their dog on the property. This makes sure that, while we want to share the beauty of the property God has blessed us with and build good relationships with our neighbours, those who walk their dogs here understand that there are also guidelines to the privilege. • The backfield and bluebell woods behind the chapel and Bramley Hall are accessible for our neighbours to walk their dogs, and if they’d like to have a coffee in the café they can tie the dog to the chain on the big tree between the café and the chapel. • Dog walkers can enter only by the back road and through the apple orchard. • Dog walkers must keep control of and clean up after their dogs. • Dogs are not allowed on the Oval road at any time. • The vast majority of people who come to walk here do this and are considerate and respectful of our facilities, and many of them express their gratitude for permission to be here. If you see anyone who does not appear to be abiding by this agreement, please feel free to speak politely to them. • For information about the DOG WALKER SCHEME see sheets in Reception. FIT MUMS & BUFF DADDIES David Hulford, a qualified personal trainer and former YWAM Harpenden resident, offers these for parents who lead busy lives. • For new or expectant Mothers there is the program ‘Fit Mums’, and ‘Buff Daddies’ (Saturday mornings) for Dads who want to exercise. • Contact David for more details: • These classes are free of charge as a blessing to YWAMers.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 63
THE BRAMLEY HALL The Bramley Hall was originally named the “Bernard Baron Hall” by the National Children’s Home. When YWAM moved to The Oval, the “BB Hall” retained its name but was changed to reflect the life of a YWAM staff member, Beryl Bramley....Beryl joined YWAM at Ifield Hall, Crawley, Sussex UK in 1973, and served faithfully through various YWAM ministries until her struggle with cancer ended in 1991. She was a pioneer, involved in many aspects of ministry, usually very practical. Beryl led the team which prepared Holmsted Manor in Sussex for the first YWAM School to be held there in 1976 and continued there as a member of the leadership team and a "spiritual mother" to many. As the years went by she took on various roles in YWAM, and worked alongside local churches. One of Beryl’s most significant ministries in YWAM was that of hospitality and catering and, as she established the hospitality ministry in Highfield Oval between 1986 and 1991, the Beryl Bramley Hall is fittingly named in her memory. Beryl’s life and ministry bore much fruit and the heart of the BB Hall remains hospitality and welcome.
STAFF POLICY FOR EATING IN THE BRAMLEY HALL Eating Together and ‘Table Fellowship’ is a very important part of our live / learn community and was modelled by Jesus and the early church. Therefore we want to make it possible for staff and trainees to eat simple, healthy and nutritious food together. Efficiency is gained in purchasing and cooking for larger numbers, but it does require greater skill and planning. Everyone who eats can contribute to the cooking or wash-‐up and cleaning of the kitchen and dining room on an equitable and consistent basis. We do want staff to see the benefit in relationship, cost and time of eating together. There should be no distinction between training staff and other staff; all are YWAM Harpenden staff. TRAINEE INPUT From the training schools budget we transfer £25 per trainee per week to the Food (FOO) account. This is spent purely on food. An additional £5 per trainee per week is for Food Equipment (FEQ), and this is used to replace broken items, purchase fridges, freezers, cookers, and maintain the dishwasher etc. CAMPUS INPUT In addition, the campus subsidises the cost of food by covering all property insurance, taxes, utilities and maintenance on BB Hall and provides free voluntary labour. These amounts are considerable. MONTHLY CHARGES Some staff eat in the BB Hall because their accommodation does not provide self-‐catering facilities, primarily those who have served less than two years on staff at YWAM Harpenden. We do not charge trainees enough to provide free staff meals, but we do charge significantly reduced amounts for YWAM Harpenden staff. Meals are substantially subsidised and take into account the fact that staff will not necessarily eat all meals there. Monthly charges are added to staff fees and transferred to the FOO account. This means that overdue staff fees will need to be addressed early. The following (2012) is a guide only, as costs will vary. • £45 per person (12 years or older) per month • 1-‐2 yrs free • 3-‐4 yrs £20/month • 5-‐11yrs £30/month • 12+ yrs £45/month • If children primarily eat main meals because they eat at school, for example, the cost will be 3-‐4 yrs £12.50/month; 5-‐11yrs £20/month; 12+ yrs £30/month. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 64
REFUNDS If you are away for two or more weeks in a month you can request, through Personnel, a refund for the time you were away, which will be calculated on a per diem figure. WASH UP ROTAS All staff eating regularly in the BB Hall will be on a clean-‐up rota with trainees and will wash-‐up or clean the kitchen at least twice per week, in addition to other work duties • The evening wash-‐up is not a “trainee work duty” or “staff work duty” but a responsibility because you are eating regularly in the BB Hall • Individuals are responsible to find their own replacement • Deep cleaning of the kitchen may be scheduled as a work duty • Breakfast and lunch prep and wash-‐up can be work duties, but work duties are to take 10 hours per week for all trainees, not just half an hour or an hour a day • Meal prep times at weekends and wash-‐up (not the main meal wash-‐up) etc should be considered as part of work duty time SIGN OUT AND SIGN IN LISTS There are two comprehensive sign in / out lists: one is for staff and trainees permanently marked as signed into the BB Hall. When not eating they would need to sign out. The other list would be for staff eating occasionally in the BB Hall to sign in. If people consistently fail to sign out and in we will need to consider consequences. • Please remember to use your proximity card to ‘beep’ in for every meal that you eat in the BB Hall, as this ensures that you eat enough meals to qualify for the reduced rate of £45 / month food charge. This includes those who don’t have cooking facilities in their residence. TAKING FOOD AWAY TO EAT ELSEWHERE Because the intention is to eat together, individuals and families should not come and take food away to eat elsewhere, except in unusual circumstances (such as illness), cleared with the Kitchen Manager. Crockery (plates, bowls, glasses, cups) and cutlery (knives, forks, and spoons) should not be taken away from the BB Hall. REVIEW PROCESS £45 / month does not cover real costs, but is the figure we are settling on for now. As we continually work to improve the system there will be ongoing review and improvements. DEFICITS ON THE FOOD ACCOUNT Wise food purchases and a healthy diet are maintained and major cost savings are unlikely. Deficits will be tackled by increasing charges to trainees and/or staff or clearing the deficit by subsidizing it from other campus sources. Miracles and free food Donations are possible with prayer and action! Compiled by John Peachey & Julia Pratten; Jan 2011 YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 65
Please be aware that this is a working document and may be updated at the end of each quarter. The initial trial was in Jan 2011. In addition to those who regularly eat in the BB Hall, all involved in food preparation or clean-‐up should participate in an annual orientation for the BB Hall, and those who oversee meal preparation will be asked to qualify for a Food Hygiene certification. Remember if you are doing any food preparation or clear-‐up you need to: • Be in good health. No cold, sore throat, vomiting or diarrhoea for 48 hours • Wear sensible closed shoes • Wear clean clothes If you have any other questions please speak to a member of the Kitchen Team.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 66
HOUSING
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 67
GUIDELINES FOR LIVING ON THE OVAL 1. Our overall consideration must be the Oval is the Lord’s property and that we are given responsibility to carefully steward this wonderful resource. Just as we have been careful to stress that it is not ultimately YWAM’s, so we all acknowledge that the housing we occupy is ultimately God’s, and we freely lay down our rights to it. 2. We believe God wants us to enjoy good quality and secure housing that will promote the well-‐being of each staff member. We want to provide a beneficial living environment conducive to the emotional, physical, spiritual and mental growth of staff, their children and the community as a whole. 3. We do our best to allocate housing without favouritism and partiality, seeking to be fair to the needs of all. 4. In YWAM, we value community. In particular, our educational philosophy is based on a live-‐learn model, where mature Christians, experienced veteran missionaries, students, long-‐term and short-‐term staff, and people of all ages and different cultures are able to interact and learn from each other. We believe discipleship and mentoring are fostered well in this environment, often occurring informally and naturally. 5. We strongly encourage practicing hospitality as it is a foundational value of YWAM. Value no. 17 states, “YWAM affirms the ministry of hospitality as an expression of God’s character and the value of people. We believe it is important to open our hearts, homes, campuses, and bases to serve and honour one another, our guests, and the poor and needy, not as acts of social protocol, but as expressions of generosity.” 6. As we live in such close proximity to one another, it is important that we respect and prefer each other. There is a base-‐wide understanding that between the hours of 11 pm and 7 am, noise must be kept to a minimum, on the Oval, in our accommodation, and in communal areas.
HOUSING FEES Rents are paid monthly in advance with, generally, an increase in January in accordance with inflation. Council Tax Council Tax is included in your rent unless you are in self-‐contained accommodation, in which case you will need to pay your council tax directly to the council. You will need to go to the website below to arrange payment.-‐and-‐benefits/council-‐tax/ Internet Approximately £10 a month for internet usage is included in your monthly staff bill. Off Campus housing You may wish to find accommodation off campus nearby, such as in Luton, St Albans, Harpenden, Batford or Redbourne. To research costs of living in the area: • or
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 68
CRITERIA FOR HOUSING ALLOCATION While the goal of the Housing Committee is to give everyone who desires Oval housing the type they prefer, it may not always be possible to do so. Due to space and financial limitations it is unlikely that ideal accommodation will be available to suit everyone on the Oval. Timing plays an important part in what accommodation is offered to incoming staff. What we can offer depends on what we have available at a particular time. The option of finding accommodation off base is open to everyone. Factors considered in housing allocation… • Length of past service to the ministries at Highfield Oval (i.e. the number of years spent at YWAM Harpenden). • Length of past service to YWAM at other locations. • Age • Length of intended service • Different needs/dynamics of families, couples, and singles. • Financial considerations. • Pastoral needs and grounds for compassion • Adequate space for people (living/cooking/bathroom) If staff members’ circumstances change, then their housing allocation is open for review, e.g. additional children, change between full time and part time service with YWAM, children leaving home. Alternatively, if accommodation becomes available on the base that was not available at the time of your allocation, all staff are welcome to apply to the housing group to be considered for a change in accommodation. The staff fee is determined by the Leadership Team and is based on the amount of space and amenities, i.e., cooking facilities, self-‐contained bathroom, etc. provided. It includes the housing, water, heat, electricity and council tax in shared accommodation. In self-‐contained flats, the Council tax is payable directly to the Council and is not a part of the YWAM fee structure.
HOUSING GROUP 1. To consider housing needs of both new applicants and existing staff, looking at available housing, and allocating as appropriate. 2. To communicate with the Flat Co-‐ordinator, department head, and the individual concerning the housing that has been allocated to them and the cost of it. 3. To approve staff moving from one house/flat/room to another. 4. To process with the ministry leader any staff departure from the Oval, ensuring that housing is left in an acceptable state. If the housing is left in poor condition, the ministry leader will be approached to help in rectifying this. 5. To check staff into new accommodation and out of old accommodation. The purpose of this is two-‐fold. 1) To ensure that the accommodation is left clean and ready for the new occupant to move into and 2) To maintain a minimum overall standard of accommodation with the expectation being that we will leave the accommodation in a similar or improved condition to how we received it. 6. To collect a Staff Fee Deposit, of £50 for single rooms and £100 for flats, that will be returnable provided that the accommodation is left in a suitable manner, e.g. keys returned, clean, no significant damage. Personnel will provide cleaning and exit
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 69
guidelines a few weeks in advance of your departure date. A member of the housing group will contact you nearer the time to arrange a check in/out visit. How do we function? The Housing Group meets monthly to serve the base community by allocating existing housing according to the guidelines in this booklet. If an issue arises that cannot wait until the next meeting, we are in regular email contact. How can the Housing Group be contacted? 1. Send a written request or e-‐mail (housing@oval.com) to say that you would like to make a housing request, express a concern or whatever. (Since we are all involved with various ministries, this is more effective than simply “a word in our ear”.) If you are aware of someone having concerns about their housing, please encourage them to contact the housing group directly. 2. Following your written request, one of us may contact you in person so you can share in more detail and depth what’s on your heart. 3. In the next monthly meeting your request will be considered by the housing group. If you feel you would like to, you are also most welcome to attend and share with us all. Please contact the chair, in advance, if you would like to do this.
DEFINITION OF OTHER ROLES INVOLVED IN HOUSING ALLOCATION Role of the Leadership Team 1. To help set priorities of allocation for the housing group (i.e. the LT may strategically reserve accommodation on base for essential staff roles or according to growth priorities. The LT may also re-‐allocate a portion of a building for major renovations or change of use). 2. To determine staff fees. 3. To input into the submission of new members and approve or appoint the chair of the Housing Group. Role of the Personnel Department 1. To bring to the Housing Group the names of staff needing to be housed. Factors such as age, length of service in YWAM, family situation, role, length of commitment to Harpenden plus any other information needed for the decision. 2. To advise the Housing Group of staff wanting to let out their flats while they are away. 3. To be aware of the new staff that departments are potentially recruiting and keep the housing group informed of staff being processed or departing. 4. To administrate staff fees, staff deposit fees, and keys to accommodation. 5. To advise of cleaning and exit guidelines for leaving accommodation and/or the Oval. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 70
Role of Ministry/Department Leader 1. To keep the Personnel Department regularly informed of staff they are recruiting or who are leaving. 2. To communicate to the Housing Group any special factors to be aware of when housing is allocated to new staff. 3. To refrain from giving any promise or expectation of the type of accommodation that might be available for prospective staff. 4. To liase with Personnel to ensure shared accommodation is adequately furnished and prepared for the arrival of the new staff. 5. To process the departure of staff with the housing group to ensure that housing is left in a suitable state. If it is not left suitably, to assist housing in rectifying this matter. Role of the Flat Co-ordinator The Chair of the Housing Group appoints the Flat Co-‐ordinator in liaison with the Housing Group and the building concerned. This role is not a permanent position for the duration of the co-‐ordinator’s time on the Oval but can be undertaken for varying lengths of time, e.g. 6 months, 1 year or longer etc. The Chair needs to be approached if there are any issues with the Flat Co-‐ordinator that you have been unable to resolve yourself, e.g. they are not fulfilling their responsibilities. The co-‐ordinator is the point person in the flat for: 1. Communicating to the rest of the flat/building when new staff are arriving (the Housing Group & Personnel are responsible for informing the co-‐ordinator of new staff & their arrival dates). The Dept/ministry leader and the co-‐ordinator are responsible for ensuring the room has basic furniture and is ready for the new staff member. 2. Welcoming new flat mates, introducing them to all the necessary information (laundry facilities, cleaning rosters and other responsibilities that are shared among occupants, TV licence information, First Aid Kit, Fire Blankets and safety procedures). Personnel and the Dept/Ministry Leader also have a responsibility to make certain the new staff member is aware of anything that would be relevant in ensuring a smooth transition to community living including cultural issues. 3. Assigning and overseeing rotas for the cleaning and upkeep of communal areas, giving job descriptions where necessary. 4. Calling house meetings or similar to help the smooth running of the little “community” 5. Making sure that any TV’s in communal areas have a current TV License. 6. Communicating any unresolved discipleship issues that arise in the flat to relevant ministry leaders with the knowledge of all concerned. (As far as possible, issues should be resolved within the flat.) 7. Communicating repair or renovation requests to the maintenance department for communal areas. Family flats should take care of their own maintenance or replacement needs. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 71
ADDITIONAL HOUSING INFORMATION Guidelines for the Temporary Holding of Staff Housing We recognise that there are situations when God leads Oval staff members to spend time elsewhere, and that sometimes it may be appropriate to hold their housing open for their return. Under the condition that God is leading them away for a specific time and purpose, with a clear call to return to long-‐term ministry in Harpenden, it may be possible to temporarily hold housing for staff. On-‐base housing is a privilege and if we hold housing for someone, the length of time granted should reflect his or her length of service to and investment in this base. Should this situation arise, please contact the Housing Group for advice. Staff must be aware though that, while the Housing Group will try to help find someone to temporarily use their accommodation while they are away to pay the rent, this may not be possible. The staff member is liable for the cost of renting of the flat while they are away should there be times when the accommodation is empty. DTS staff going on outreach who have made a two year commitment to the Oval are allowed to hold their accommodation until their return and be charged at 50 per cent of their normal rent plus council tax. This is up to a maximum of 3 months. Alternatively, they may look to sub-‐let their flat to another YWAMer whilst they are away. They will need to pack belongings away to adequately allow for someone to use their room during their absence. However, if the DTS is assisting staff financially with outreach costs, this rent reduction will not apply. Staff who do wish to apply for this rent reduction need to notify housing at least two weeks before going on outreach. Storage on the Oval Some of the buildings have communal storage areas (a room or cupboards). These should be shared equally between all the occupants in that building/corridor, including those in shared and self-‐contained flats. However, if you do have more storage space in your accommodation than others, please take this into consideration when using the communal storage space. Subletting your Room/Flat If you are subletting your flat for more than a week, PLEASE let the Housing Group and Personnel know. This is so that we know who is actually living on the Oval at any given time for security, post, etc. If you wish to sublet to anyone outside of the Oval Community, there must be approval from the leadership team.
WHAT CAN BE EXPECTED IN SHARED ACCOMMODATION Kitchens Tables and chairs, cooker, fridge/freezer, cupboards, pots/pans, and floor covering. Bedrooms Bed, wardrobe, chest of drawers, lamp/light shades, curtains, chair, table, basic floor covering (some variation on these items will be provided). Laundry Areas Washer/dryer YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 72
Lounge Area Sofa/chairs If residents of flats wish to have microwaves, kettles, toasters, TVs, VCRs, etc., they are free to purchase them as individuals or jointly. TV licenses are required for the communal room in each individual flat and for any private TV kept in your bedroom. These may be obtained at the Post Office or online at. Cookers and other major appliances are maintained and replaced by YWAM, unless negligence is involved. Please contact the management team regarding any replacements. The Flat Co-‐ordinator should submit to the Refurbishment Group in writing any improvements they desire concerning communal areas.
WHAT CAN BE EXPECTED IN SELF-CONTAINED ACCOMMODATION? Kitchens Basic Kitchen items -‐-‐ cooker, cupboards and sink are provided by the Oval. Often due to the generosity of the previous occupants, most, if not all, flats have reasonable kitchens. Bathrooms Sink, Bath or Shower and Toilet Bedrooms and Lounges Normally these are provided empty so that residents can either bring their own furniture or obtain furniture when they arrive. Note: Exact details of what the flat does and does not contain can be requested from the Housing Group at the time of Oval Housing allocation. It should also be noted that the Oval keeps a very limited amount of furniture stock on site. This usually consists of beds, sofas, cupboards, wardrobes, etc., and can be reserved by any potential residents, if available at that time.
PAINT POLICY ON THE OVAL We want to encourage everyone to feel at home in their accommodation and to have the freedom to decorate as they would like. However we have found that it is necessary to have some guidelines with regards to re-‐decoration (paint & wall-‐paper) which we ask you to respect. If you have any questions with regards to painting/decorating your accommodation please approach a member of the Refurbishment or Housing Group (the details of who are in these groups is on the Intranet). In light of us all being stewards of this property we would ask that you help maintain your accommodation to a high standard. This means painting as needed in order to keep the accommodation in a good condition. When rooms are re-‐painted/get new wall-‐paper, it is expected that this is done with the appropriate preparation and finish. Please get advice if you are not sure what this entails. Resident’s own rooms/self-contained flats
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 73
1. Rooms should be painted in neutral or pastel colours. If you are not sure if the paint you like is suitable, please check with a member of the Housing or Refurbishment group before painting. 2. If you choose to paint your room in bright colours this must be painted back to a neutral colour before you move. However you are only allowed to paint the walls/ceiling in bright colours. Please bear in mind that it may take 2-‐3 coats of paint to cover bright/dark colours which is at your own expense. 3. Radiators, pipes, window frames, doors and door frames are only allowed to be painted in white or magnolia or the wood can be left unpainted if it is properly treated with either varnish or wax to protect it. 4. If your window/door frames were unpainted when you moved into your accommodation, then you are not allowed to paint them. This is because it is a very time-‐consuming process to strip them of the paint and also leaving them unpainted requires less upkeep. However you are able to put varnish/wax on them to protect them. 5. If the new residents like your bright colour scheme and request that you leave it, then they are responsible for repainting the room back to neutral colours when they move. 6. We are aware that some rooms were inherited with bright colours and in these cases, the base will provide magnolia or white paint for these to be repainted. 7. All painting, apart from the exception above, is undertaken at your own expense. 8. All of the above also applies to re-‐decorating with wall-‐paper instead of paint. 9. If a member of staff leaves having not re-‐painted their room back to neutral colours, the line leader will be approached and asked to do this with their team. Communal Rooms The base will provide magnolia or white paint for the communal areas in the buildings. If you would like to add a mixer to this or purchase a different colour this is at your own expense. However communal areas must be painted in neutral colours and hall-‐ways must be consistent. Before painting any communal areas, a request needs to be made to the Refurbishment group.
REFURBISHMENT GROUP The refurbishment group exists to advise on and approve changes to the fabric of residences, common areas and offices on the Oval, whether funded by the Oval or by individuals. While the Oval is your home when living here, it remains the property of YWAM Harpenden when you leave. For this reason, the refurbishment group will work with staff towards the improvement of our facilities within the parameters of our limited resources. The refurbishment group will consider long and short term implications of any change, including: legal requirements; financial limitations; and other needs on the base; as well as the value to the current and future users of any rooms. It is likely that most changes you wish to make, which you are going to fund, to improve your living space will be approved. The group exists mainly to direct base-‐funded improvements and to ensure that all work is done in-‐line with legal requirements or plans for the long-‐term use of an area.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 74
Therefore, any changes you propose to make to the Oval buildings in the following categories need to be approved by the refurbishment group. This can be done by a simple email to refurbishment@oval.com. Things you need to get approval for : • Any work involving changes to the electrics -‐ remember, the refurbishment group does not deal with repairs to existing items, but with changes you wish to make to improve them. Note: this does not mean changing light bulbs or lampshades but does include the changing of fixtures. • Any plumbing work Note: Plumbing in major appliances can be done by a professional, or done by yourself as long as you have it checked by the maintenance team or a recognised competent person. Improperly fitted appliances can cause major damage. We recommend that you ask the refurbishment group and seek competent advice before installing any major appliance (fridge, freezer, dryer, washer, dish-‐washer) that is not just the replacement of an old one. Note: This is not referring to the repair / maintenance of existing plumbing, which should be referred to maintenance@oval.com. • No work involving changes to the gas mains/supply should be attempted under any conditions. This includes installation of gas-‐fuelled appliances. This is a legal requirement, whereby all gas appliances are to be handled by CORGI registered professionals. • Any building work which creates a permanent change (ie. Dividing rooms, building loft beds, fitted wardrobes etc) • Floor Coverings -‐ any permanent changes made to floor coverings need to be approved. The base attempts to provide adequate floor coverings in common areas and rooms. If a floor cover needs changing, make a request and we will make the decision together. If you wish to fund the change of a floor covering it can be done with the approval of the Refurbishment Group on the understanding that you are investing in the Oval and will leave the carpet/floor on your departure. • Decorating -‐ The base attempts to provide window coverings (curtains, blinds etc.) for each flat. These can be replaced as long as you provide adequate window coverings, of equal or greater value, when you leave – i.e. you can either leave the ones you buy, or put up the originals or similar ones. Therefore, no permission is needed to replace window coverings that can easily be changed.
EMERGENCIES AND REPAIRS Emergencies Who do I call on for Emergencies? The Maintenance person or in the absence of one, the Leadership Team/Management Team. (Note: emergencies are things like: floods, total power failure, fire, no heat, etc., NOT general repairs) General Repairs YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 75
The Oval is responsible for the water, gas and electricity, as well as sanitation, space and water heating. This includes the following: INTERNALLY • Water pipes, gas pipes and electrical wiring. • Basins, baths, toilets • Water heaters, boilers, fireplaces (structures) and radiators • Electrical sockets and light fittings, but not light bulbs and fuses. • Walls, floors, ceilings, doors, door frames and thresholds EXTERNALLY Roof gutters and drain pipes Outside walls, doors, window frames and other external timbers. External painting. Pathways and stairs Note: For those with fireplaces, please note that you are responsible to sweep your chimney at least once a year. You MUST notify the Housing Group when your chimney is swept as the Oval must keep a record for insurance purposes. Please DO NOT light a fire until this has been seen and approved. Procedure for Reporting a Repair Request Please email: maintenance@oval.com The Maintenance team is usually very busy and have to prioritise requests. Please be patient and gracious with them. Note: Under no circumstances WHATSOEVER, should residents attempt ANY repairs, modifications, or upgrades to the Oval maintained areas, particularly water, electricity or gas. If in doubt, please ask.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 76
LOCAL TRANSPORT
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 77
DRIVING & CARS CARS If you plan to be in the UK for some time, you may consider buying a car. Remember that you can purchase a second-‐hand or used car more cheaply than a new one! It is a good idea to take a British friend along with you to help you check it out. Having a car can work out to be expensive, as you will need petrol, insurance, and motor tax, as well as paying for repairs. MOTORISTS ON THE OVAL Please drive slowly around the Oval and take heed of the 10-‐mile speed limit. This is for the safety of young children around the base – who can easily come from behind a tree, parked car or hedge without seeing you or your car. PARKING ON THE OVAL • Please park your cars in the parking bays in front of your home. • If you have more than one car, please park your second car behind the Bramley Building or down by the Clock Building car park. • Please ask all visitors (personal or business, daytime or night-‐time) to use the car park behind the Bramley Building. That way the parking bays remain free for residents when they return home. LEGAL INFORMATION FOR FOREIGN NATIONAL DRIVERS United Kingdom law requires that after one year of residency in the U.K., a foreign national wishing to continue driving in the U.K. MUST OBTAIN A BRITISH DRIVING LICENCE. For further information, please see website:. If you need to get a British driving licence and take a driving test, this can take several months, so plan well before your year comes to an end. • IMPORTANT - Foreign nationals must carry their driving licences on them at all times. If asked to produce it and unable to do so, the police will arrest you until you can prove that you are licensed to drive. • PLEASE NOTE: If you are driving on the wrong type of driving licence and you have an accident, it is possible that the insurance company will make VOID the insurance cover you have! The implications of this are serious in that a substantial financial claim could be levied against YOU, which in the natural would be impossible for you to pay. The results could even get you a prison sentence. The moral issue, of course, would also be that the ‘Third Party’ having a legal claim to recompense would get nothing, thereby possibly causing great family hardship. • If your licence shows entitlement to drive heavy goods or public service vehicles (HGVs/PSVs), please note that special arrangements apply to the driving of these vehicles in Great Britain. You may only drive these vehicles if: - You are the holder of a licence issued by a Member State of the European Community or the vehicle you are driving has been temporarily imported. • You must bear a licence that allows you to drive a vehicle with more than nine total people before you are allowed to legally drive vans. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 78
CAMPUS VEHICLES As a campus, we have vehicles available for business purposes, and at times for personal use. If you would like to be included on the insurance to drive these vehicles, please see the Campus Administrator. Only authorised drivers may use the campus vehicles. Some of the conditions for the drivers are below. Otherwise, further information can be obtained from the Campus Administrator. • There are weekly sign-‐up sheets for each vehicle near where the vehicle keys are kept. It is necessary to book a vehicle and to indicate whether the trip is a business or a personal one. Should a vehicle be required for business and no booking space is available, business use will take precedence over a private booking. • In order to use the campus vehicles speak to the Campus Administrator to ensure that you’re eligible and put on the insurance. • Should you wish to book a vehicle for a long period (over 4 hours), please check with the Campus Administrator first and then record it on the sign-‐out sheet. • Please fill each vehicle with fuel when it reaches ¼ tank level and take note if the car requires diesel or unleaded fuel. You may get reimbursed for any fuel you paid for from the accounting department if you have a receipt for the fuel. • Please check the oil and water before you take a vehicle out. • Rates for Private Use: (2012: costs will increase in line with fuel costs) - Volvo car: 36p per mile + 20% VAT - Renault Transit Van: 60p per mile + 20% VAT • Please note: These prices may change regularly, due to rises in petrol prices. WHAT TO DO IF A YWAM HARPENDEN VEHICLE BREAKS DOWN? • YWAM Harpenden belongs to the Royal Automobile Club (R.A.C.). • There is a membership card in each vehicle. • If you break down, ring the FREEPHONE (0800) number on the back of the card. The RAC provides ‘at home’, roadside and recovery assistance. Please make sure the card is kept in the vehicle to which it belongs. If you breakdown and the card is missing, it will be difficult to get service. You could be the one stuck on the motorway! USE OF MOBILE PHONES IN VEHICLES – IMPORTANT, TAKE NOTE! In a new regulation that came into force on the 1st of December 2003, it is a specific offence to use a hand-‐held phone, or similar device when driving. A hand-‐held device is something that “is or must be held at some point during the course of making or receiving a call or performing any other interactive communication function”. The law will also consider employers liable if they require their employees to use a hand-‐ held phone whilst driving and might also be liable if they failed to forbid their employees from using phones whilst driving on company business. Whilst Youth With A Mission is not an employer in the traditional sense, we do not endorse any staff member breaking this law.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 79
TRAINS & TRAIN TRAVEL The rail network provides a fairly fast way of travelling around the country. You can find out information about train times and ticket prices from National Rail Enquiries: • Web: or from a train station or travel agent. • You can buy train tickets from any train station. • Harpenden Train Station, Station Road, Harpenden, Herts. AL5 4SP • Web: IDEAS FOR CHEAPER TRAIN TRAVEL Buy a Return Ticket Return tickets are usually cheaper than two single tickets. If you are travelling to/from your destination in one day, you may be able to buy a ‘cheap day return’, which is even cheaper. Buy your ticket in advance If you plan to make a long journey, it is often worth buying your ticket a few days, or even weeks, before your journey – this will save you money and should ensure you get a seat on the train. The tickets you can buy in advance include Saver, Super Saver and Apex tickets. For some of these tickets, you will need to book the time of train you will travel on – your ticket will not be valid if you travel on a different train. Travelcards/Season Pass If you intend to travel around London or any of the major cities, it will probably be cheaper to purchase a travel-‐card. A one-‐day travel-‐card allows you unlimited travel for one day, and normally works out to be the price of three journeys! In London, you can buy an off-‐peak travel-‐card, Mon-‐Fri after 09.30, or weekends. You can also buy a travel-‐card for weekdays before 09.30, but these are much more expensive. You can also buy travel-‐cards / season tickets for longer periods, e.g. a week, a month, a year for travel in lots of towns / cities in the UK. • Network Card: In the South East of England, a ‘Network Card’ works out cheaper (at the time of writing) than other discount cards, such as the Young Person’s Railcard. • Young Persons Railcard: If you are 26 years old or younger or a full time student, you can buy a Young Person's Railcard. This gives you a 1/3 discount every time you buy a train ticket, so it is worth getting one if you intend to travel a lot in the UK. You can buy one at most stations. • Ask for help: ask at the train station which would be the best ticket or you – and compare the costs of the different types of tickets available. TRAIN STATIONS IN LONDON Many cities around the UK have just one main railway station. However there are eight main stations in London, from where you can catch trains to different parts of the UK. It is wise to check which station you will need to use if you are travelling through London to get to another city. Trains from Harpenden stop at Kings Cross / St Pancras International Station. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 80
UNDERGROUND TRAINS Several cities in the UK have an underground or metro system (in London, this is called the . OYSTER CARD When visiting London by train, you can purchase an Oyster card -‐ a plastic smartcard to use instead of paper tickets. You can put Travel-‐cards, bus & tram passes and pay-‐as-‐you-‐go credit on it, which you use up as you travel. Staff at the Harpenden train station will help you buy the most cost-‐effective ticket. Travelling in groups of four will save you money.
LOCAL BUSES You can find leaflets with local bus routes and times at the public library, or find information on routes and times of buses in your area from Traveline (). • Many buses in large towns and cities operate an ‘exact fare’ policy, which means the driver will not give you change if you don't have the right amount of money in coins. • Make sure that you have a selection of coins ready before you board the bus. • You may be able to buy a travel-‐card or season ticket to save money if you use local buses regularly. • To catch a bus, find a bus stop for the right bus route. When your bus approaches, show the bus driver that you want to use the bus by stepping to the edge of the pavement and stretching your arm towards the road. • Pay the driver, or show any travel-‐card / season ticket as you get on the bus. • When you want to get off, press the button that tells the driver to stop at the next bus stop (ask the driver for help if you don’t know where you need to get off the bus – the bus driver will then tell you when you reach your destination).
LONG-DISTANCE COACHES •
•
•
• •
National Express, a national coach operator, operates a comprehensive network of coach services across the UK and this can often work out cheaper than other forms of travel. However, travel by coach takes longer, may not be as comfortable, and often has fewer services. If you are 26 years old or younger or a full time student, you can buy a Discount Coach-‐card. This will save you 30% on many National Express journeys. Book your ticket in advance, as seating is limited. For more details, visit your local coach station or contact National Express (Web:) An alternative company, Megabus also offers very cheap coach travel across the UK. You can also travel by coach to destinations in continental Europe – services are run by Eurolines. These coaches always start and finish at London Victoria coach station.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 81
TAXIS Sometimes you need to travel where there are no buses or trains, and then taxis are useful. • Look for taxi companies in local telephone directories. All taxi firms have to be registered by the local council, so for short journeys different taxi companies will charge similar fares. However, always get a quote before a journey of more than 8 miles as prices can vary a lot between different firms. • Taxis are often thought to be expensive, but if a group of people share a taxi and divide the cost, the price will work out quite favourably. • For your own safety, only travel in a registered taxi. • Do not enter a car if you cannot see a taxi sign, even if the driver offers you a cheaper fare.
HITCH-HIKING (GETTING A LIFT)
•
Asking lifts from strangers in passing cars is known as hitch hiking.
•
Hitch hiking is not considered safe in the UK, especially for women or people travelling alone.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 82
HEALTH, DENTAL & MEDICAL
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 83
EMERGENCY SERVICES & MEDICAL CARE The following emergency services can all be contacted on any ‘phone by dialling 999. On the Oval, this bypasses the need for a code for an outside line and automatically connects you to the emergency services. They will ask you which service you would like. • Police • Fire • Ambulance / paramedic • Coastguard If you call the emergency services, please be aware that after 22:30 they need to be let in at the back gate – they may not know the code. Also you need to know your building and flat number.
HEALTH & MEDICAL INFORMATION BEFORE YOU ARE ILL! Don't leave finding out about health care until you don't feel well! • One of the first things to do on arrival in the UK is to find out if you are eligible for NHS (National Health Service) treatment. The NHS is the public health care system in the UK. You should register with a local doctor (General Practitioner / GP). IF YOU ARE ILL • First visit the surgery of the doctor with whom you wish to register. You will be sent somewhere else if they cannot help you. You may need to make an appointment to visit the doctor at a later time. • Call the NHS 111 service if you need medical help fast, but it’s not a 999 emergency. •
You will be assessed, given advice and directed straightaway to the local service that can help you best. Calls to NHS 111 are free from landlines and mobile phones.
•
You can also contact to check symptoms online. NHS walk-‐in centres provide assessment by experienced nurses or doctors (not all have a doctor) without an appointment. They offer advice and treatment for minor ailments and injuries such as cuts, bruises, minor infections, skin complaints etc. Luton Walk-In Centre 14-16 Chapel Street, Luton, Bedfordshire, LU1 2SE (4.3 miles).
•
MINOR INJURIES UNITS If your injury is not serious you can visit a minor injuries unit (MIU) rather than an A&E (Accident & Emergency) department; this allows A&E staff to concentrate on people with serious and life-‐threatening conditions and save yourself a potentially long wait. (For definitions of serious injuries or illness, see next section) Sprains and strains Broken bones Wound infections Minor burns and scalds Minor head injuries Insect and animal bites YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 84
Minor eye injuries Injuries to the back, shoulder and chest 1. St. Albans City Hospital Minor Injury Unit, Waverley Road, St. Albans, Hertfordshire, AL3 5PN Tel: 01727 897182 (4.6 miles) 09.00-‐20.00 7 days a week (closed Christmas Day) 2. Dacorum Urgent Care Centre Hillfield Road, Hemel Hempstead, Hertfordshire, HP2 4AD Tel: 01442 287451(7.0 miles) 24hrs/ 7 days a week.
ACCIDENT & EMERGENCY (A & E) A & E departments assess and treat patients with serious injuries or illnesses, such as.... Loss of consciousness Pain that is not relieved by simple analgesia Acute confused state Persistent, severe chest pain, or Breathing difficulties If you need to go to A&E, somebody on campus with a car will help you if necessary. • If you are unable to move to a car or need emergency onsite care -‐ call 999 NEAREST A&E: Luton & Dunstable Hospital: Lewsey Road, Luton, Bedfordshire, LU4 0DZ Tel: 0845 127 0127 (6.9miles) Queen Elizabeth II: Howlands, Welwyn Garden City, Hertfordshire, AL7 4HQ Tel: 01438 314 333 (8miles) PAYING FOR HEALTHCARE AND PRESCRIPTIONS Emergency treatment in A & E or from a local doctor (GP) is free, but you may need to pay for other health services and prescriptions. If you don’t register with a GP, costs are much higher. DO I NEED HEALTH INSURANCE WHILE I’M IN THE UK? Emergency treatment at a hospital is normally free of charge. When taking up residence in the UK, you are advised to register with a GP and a dentist. Once you are registered with a GP, you receive an NHS card with an NHS number. For volunteers and missionaries living here for under a year, they may need to pay some fees when admitted to hospital as an in-‐patient or seen at an outpatient clinic. If you have lived in the UK for at least a year prior to treatment with no more than 3 months out of the country in 12 months, you are entitled to free NHS treatment. If you have questions, visit: PRESCRIPTIONS During your visit to the GP or dentist, you may be given a prescription describing the medicine you need: Take the prescription to a shop which has a ‘pharmacy’. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 85
The shop will supply you with the medicine for which there is usually a charge. If you have an exemption certificate you do not need to pay for your prescriptions. MEDICINES You can buy some medicines for common ailments at a supermarket or chemist / pharmacy. In a pharmacy, you can also ask for advice if you don't feel well, for example with a headache or sore throat. However, if you continue to feel unwell, you should see a doctor. PRIVATE TREATMENT It is also possible to have medical treatment ‘privately’, i.e. paid for by you rather than the NHS. Talk to your doctor for details. You will obtain treatment more quickly if you have private health cover than through the National Health Service, although the treatment itself will probably be the same. Be warned: private treatment can be very expensive. SICKNESS • If you, or a ‘neighbour’, are ill and unable to come to work, please see that the appropriate department head is informed as soon as possible. Please also let Personnel or the Leadership Team know about serious illnesses so that they can come and pray for you. GENERAL MEDICAL PRACTITIONERS We strongly recommend that all of our staff register with one of the two medical centres in Harpenden. If you are not from the UK and don’t have an NHS number, you may need a letter from Personnel confirming that you are living here. The Elms Medical Centre Tel: 01582-‐769393 Appts: 01582-‐767444 5 Stewart Road Fax: 01582-‐461735 Harpenden AL5 4QA Davenport House Surgery Tel: 01582-‐767821 Bowers Way Fax: 01582-‐769285 Harpenden AL5 4HX When booking Dr’s appointments, please schedule these outside of office hours. DENTISTS Dentists specialise in the treatment of teeth. You may choose any local dentist. • Ask before you start treatment if it will be paid for by the NHS or not. If you have an exemption certificate (see above) you do not need to pay for dental treatment. • It is worth asking about dentists before you need them! For more information on dental costs see:-‐fees-‐nhs.php OPTICAL TREATMENT YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 86
If you need eye glasses, go to any specialist optician or high street optician. • Compare prices at several shops before having your eyes tested or buying glasses, as some shops are more expensive than others. FIRST AID There are several qualified First Aiders on staff, trained to assist in accident situations only. • The names of those trained in First Aid are in Reception and inside First Aid boxes. • Please refer any other personal medical questions to your General Practitioner (GP). Basic First Aid kits are located in every building on the Oval for the use of staff for work related injuries only. Staff and students are expected to provide their own private medical supplies for pain relief, plasters (band-‐aids), etc. All work / ministry related accidents must be reported in the Accident Log in Reception as soon as possible after the accident.
LOCAL CHURCH FELLOWSHIPS YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 87
We are all part of the Body of Christ and as part of our Foundational values we are called to: “Fellowship: We are called to commit to the Church in both its local nurturing expression and its mobile multiplying expression.” Below are local churches which YWAM Harpenden staff attend. Alongside regular church attendance, active participation is encouraged (e.g. in a small group or serving). Please let Personnel know which church you join as this helps us with local church relationships. For all local churches see the following websites: or or Harpenden ALL SAINTS (Church of England) Sunday: Holy Communion: 09:00, Family Service: 10:15 Activities: Tots & Teddies, Sunday Clubs & Youth Groups Home Fellowship Groups, Prayer Groups, Choir, Women’s Fellowship. 129 Station Road, AL5 4UU Tel. 01582 765524 (St Nicholas Office) BETHANY COMMUNITY CHURCH (New Frontiers) Sunday: 10:30 at the Chapel, St George’s School Midweek Cell Groups, and Youth Activities Elders: Neil Chitty, Tony Foord and Steve Low
Natalie Edwards & family
Doreen Jenkins Amanda Costa & family
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 88
Office: 130a Southdown Road, Harpenden AL5 1PU Tel. 01582 763860 email: info@bethanycc.org.uk CHRISTCHURCH (Independent Evangelical, FIEC) Sunday: 10:30; Roundwood Park School, Roundwood Park 18:00 at Christchurch Vaughan Road Rev Gareth Lewis Tel: 01582 463260/768289/769165 House groups, Alpha, Christianity Explored, Youth activities.
HIGH ST. METHODIST Sunday: 10:30 & 18:30; full range of midweek activities Rev Jenny Dyer, Church Office: 01582 713056 On the High Street, next to WHSmith CRABTREE CHURCH (Independent Evangelical, Crabtree Lane) Mike Read Tel: 01582 769724 NETWORK CHURCH Sunday: 10:30 (cell church working in association with Pioneer) Rothamsted Conference Centre, on the Harpenden Road. For location map and more information visit our website or phone Trevor Withers, leadership team leader, on 01727 858379. CELL CHURCH (weekday house church) Contact the Greens directly to get details of when they meet. ST NICHOLAS (Church of England) Sunday: 08:00 Holy Communion 09:30 Sung Eucharist (with Sunday Club and Crèche) 11:30 Morning Praise 16:30 'Simply Worship' -‐ first Sunday of the month 18:30 Evensong Rector: Rev Christopher Futcher Parish Office: Tel 01582 765524 / Fax 713646 email: office@stnicholasharpenden.org.uk
Anne & Brian Sloan Val Clark
Terry Elphick Jon & Leah Judge & family John & Suzi Peachey & family Steve & Julie Sullivan & family Ina Steyn Danny & Rachel John & family
Caleb McAlpine
Emmanuel & Janice Entee Pete & Pat Kinahan
Lynn & Marti Green Lydia Chua Becky Mehaffey
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 89
UNITED REFORMED CHURCH Sunday: 10:30 Contact Tom Pattie for all enquiries: 01582 760987 Vaughan Road Linked with Trinity URC St Albans and Brickett Wood URC. Other services and activities-‐urc.co.uk THE SALVATION ARMY Church Office Tel: 01582 469399 (mornings) Email: shja@waitrose.com Leyton Green OUR LADY OF LOURDES CHURCH (Roman Catholic) Priest: Monsignor Harry Turner Parish Office: 1 Kirkwick Ave Tel: 712245 Rothamsted Avenue Luton NEW COVENANT FELLOWSHIP CHURCH Kestin House – (All Saints Building) ST MARY’S (Church of England) Sunday: 08:00 -‐ Holy Communion 10.00 -‐ Morning Worship, family focused 18:33 -‐ evening service oriented to young people 19 Dunstable Road Luton, LU1 1BE Contact: Tel: 01582 438 200 CHRISTCHURCH BUSHMEAD (Church of England) Sunday: 08:00 Holy Communion (2nd and 4th Sunday only) 09:30 Informal Worship with groups for all children up to Yr 6 11:15 Informal Worship with groups for children up to Year 10 Hancock Drive, Luton, LU2 7SF Tel.: 01582 454081 Email: office@christchurch-‐bushmead.org.uk Website:-‐bushmead.org.uk LUTON CHINESE CHURCH Sunday: 14:00 Central Baptist Church 52 Park Street, Luton LU1 3ET Tel.: 01908 694114 Fax: 01908 675512
Gareth & Cindy Cater & family Daniel & Wendy Snell & family
Annette Jandrell
Andrew & Nice Bowers & family
Yan Yan Liu
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 90
Email: lutonccc@yahoo.com LUTON CHRISTIAN FELLOWSHIP Corner of Hibbert St & Castle Street Luton, Bedfordshire LU1 3AL 01582 619 990 STOPSLEY BAPTIST CHURCH Sunday: 10:25 & 19:00 St Thomas’ Road, Stopsley, Luton, LU2 7UY Tel.: 01582 727352 Fax: 01582 418357 Email: office@stopsley.net Website: HOPE CHURCH Email: mail@hopechurch.co.uk Website: ST ALBANS ST PAUL'S CHURCH Hatfield Road, St Albans, AL1 4JP Office, Blandford Road, Telephone (01727) 846281-‐stalbans.org THE VINEYARD CHURCH Sunday: 10:00, 11:59 & 19:45pm Unit 7, Brick Knoll Park Ashley Road Industrial Estate St Albans AL1 5UG Tel: 01727 812 765 ST ALBANS ABBEY CITY CHURCH
Dale & Emma Lambert & family Chris & Laura Mudd & family
Yan & Claire Nicholls & family
Colin & Halyna Forbes & family
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 91
HARPENDEN & THE LOCAL AREA
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 92
HARPENDEN is a picturesque and lively town in Hertfordshire, South-‐East England, just 35 miles north of London, which is easily reached by train. With over 30,000 residents for which the Town Council provides essential community services, ‘the Village’ as it is referred to locally, has good transport links, an abundance of shopping, leisure and restaurant facilities and many green open spaces, of which the Green Flag award-‐winning Harpenden Common is the largest. Harpenden is also home to the world-‐renowned Rothamsted Research Centre where scientific research focuses on sustainable land management and its environmental impacts. Rothamsted Park has a small skate park, tennis courts and fitness centre with a public swimming pool. Enquire at the Fitness Centre or pool for opening times and costs. Harpenden has many shops commonly found in other English towns, with three central supermarkets, multiple female clothes shops, charity shops, banks, estate agents and chemists. A good proportion of these are run by independent retailers. The local council has resisted the opening of fast food chain outlets. Cafes are common in Harpenden and most are owned independently. There are multiple restaurants and many pubs; both in central Harpenden and in its suburbs.
TOWNS AND CITIES NEARBY ST ALBANS (5 miles south of Harpenden) St Albans town forms the main urban area of the City and District of St Albans. St Albans was a settlement of pre-‐Roman origin named Verlamion (or Verulam) by the Ancient British Catuvellauni tribe. It became the first major town on the old Roman road of Watling Street for travellers heading north and became the Roman town of Verulamium. Saint Alban, the first British Christian martyr, was beheaded in AD 308 by Maximian at the orders of Emperor Diocletian, who had denounced the Christian faith and ordered the deaths of all subjects and allies of the Roman Empire who refused to give up the faith. Saint Alban consequently gave the town its modern name. It is a historic market town, and is a sought-‐ after dormitory town within the London commuter belt. Property prices are notoriously high within the district, which is one of the most expensive in the UK. • Public transport to St Albans is via bus or train. LUTON (7 miles north of Harpenden) Luton is a large town and the unitary authority of Bedfordshire, England. With its near neighbours, Dunstable and Houghton Regis, Luton forms the Luton / Dunstable Urban Area with a population of over 240,000. Luton is home to Luton Town Football Club (whose history includes several spells in the top flight of the English league as well as a Football League Cup triumph in 1988), London Luton Airport (opened in 1938, one of England's major airports), and the University of Bedfordshire. Luton has seen several waves of immigration; in the early 20th century Irish and Scottish people arrived in the town, followed by Afro-‐Caribbean and Asian immigrants. More recently, immigrants from Eastern YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 93
Europe have made Luton their home. As a result of this Luton has a diverse ethnic mix. Luton Carnival, held on the late May bank holiday, is the largest one-‐day carnival in Europe. The town was for many years famous for hat-‐making and home to a large Vauxhall Motors factory; the head office of Vauxhall Motors is still situated in the town. Car production began in 1905 and continued until 2002, but commercial vehicle production remains. The main shopping area in Luton is the Arndale Mall. George Street, on the south side of the Arndale, was pedestrianised in the 1990s. Contained within the main shopping centre is the Market, with butchers, fishmongers, fruit and veg stalls, hairdressers, tattoo parlours, ice cream, flower stalls, and T-‐shirt printing as well as eating places. Another major shopping area is Bury Park where there are shops catering to Luton's ethnic minorities. • Public transport to Luton is via bus or train. LONDON The capital of England and the United Kingdom, the largest metropolitan area in the United Kingdom, and the largest urban zone in the European Union by most measures, London has been a major settlement for 2,000 years, with a history going back to its founding by the Romans, who called it Londinium. London's ancient core, the City of London (the financial district), largely retains its square-‐ mile mediaeval boundaries. Since at least the 19th century, the name London has also referred to the metropolis around this core and within the boundary of the M25 motorway. The bulk of this forms the London region and Greater London administrative area. The Greater London Urban Area is the second largest in the EU with a population of over 8 million, while London's metropolitan area is the largest in the EU with an estimated total population of between 12 and 14 million.-‐visited city in the world: London's five international airports make its airspace the busiest of any urban centre worldwide, and London Heathrow (LHR) is the world's busiest airport by number of international passengers. London's 43 universities form the largest concentration of higher education institutions in Europe. In 2012, London became the first city to host the Summer Olympics three times. London has a diverse range of peoples, cultures and religions, and more than 300 languages are spoken within its boundaries.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 94
MAP OF HARPENDEN
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 95
LIVING IN BRITAIN
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 96
SETTLING IN Even though YWAM Harpenden is an international community, and you may not fully notice cultural differences until you are in a truly British context, moving to a new country can be daunting and difficult. Everything is unfamiliar; the weather, landscape, language, food, dress, social roles, values, customs and communication -‐ basically, everything you're used to is no longer there. You'll find that the day unfolds differently to where you come from, that business is conducted in a way that may be hard to understand, the shops open and close at hours that you could never predict…BUT we want to do our best to help you settle quickly!
BRITISH CULTURE The English are said to be reserved in manners, dress and speech and are famous for politeness, self-‐discipline and especially our sense of humour. Basic politeness such as, ‘please’, ‘thank you’ and ‘excuse me’, are expected. CASUAL CONTACT British people do not always make prolonged conversation on a first meeting. This is called being ‘reserved’. You will find that most local people won’t talk to strangers while shopping, on the bus, train or when in a queue. You should not interpret this as being unfriendly, although it may seem strange to you. You should not try to make continuous conversation at such times unless it is obvious that the other person expects it. A FIRST MEETING On first meeting someone, try to ask general questions and not personal ones which may be thought to be impolite. Questions like, ‘What is your name?’ ‘Where do you live?’ or ‘What do you do?’ are acceptable, but questions like ‘How old are you?’, ‘How much do you earn?’ or ‘How much did you pay for this?’ would be considered impolite. If in doubt, talk about yourself: what you do and where you come from. Some British people know little about other countries, and many know little about other cultures in detail. Even if they have travelled abroad, tourist travel is very different from actually living in a country. TERMS OF ENDEARMENT - NAMES YOU MAY BE CALLED. TIME Time keeping is quite rigid in the UK. Life revolves around our watches and clocks and dominates everyday life! Arriving late, even a few minutes, is considered impolite. For example, if a meeting is arranged for lunchtime, there might be a plan to eat and then to talk or the other way round. If you are late you could miss the part you needed to attend. TOUCH The British are reluctant to show their emotions in public. Unlike some cultures, people do not usually slap each other on the shoulder or make physical contact during a conversation. A British person may misinterpret such behaviour as aggressive or being too emotional. • It may be usual for you to stand close to another person while in conversation. In the UK people usually maintain a distance of 60-‐110 cm, so do not be surprised if people move away from you when talking! YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 97
GREETINGS Most British people will smile when they meet you, irrespective of how they are feeling. They will often greet you with ‘Hello, how are you?’ This is simply a way of saying ‘Hello’ or ‘Welcome’ and they will be expecting a reply similar to ‘Quite well thank you’. ‘Hello, how are you?’ is not a request for a lot of details about your health. • In a more formal situation (such as meeting your tutor or landlord for the first time) it is usual to shake the right hand of the person you are meeting. It does not matter if you make the first move with your right hand. • Kissing / embracing are not usual on a first meeting and you should avoid them. • In the UK, there is no special significance to the left and right hands. Both can be used for giving and receiving presents, although the right hand is always used for shaking hands. You may be used to avoiding eye contact as a sign of respect for an older person or authority figure. This is not the case in the UK where avoiding eye contact is seen as a sign of insincerity and slyness. Try to look at people when speaking to them although it is usual to avoid prolonged eye contact with strangers (for example the person next to you in a train). GENDER AND EQUALITY It is important to be aware that in the UK female and male members of staff are equally respected and accepted. HOW TO ADDRESS PEOPLE You may be thought very formal if you address people as Mr, Miss, Mrs, Dr or Professor, as many people now expect to be called by their first names; however, some older people may prefer to be addressed more formally -‐ listen carefully to how people introduce themselves and to how others address them. QUEUES Queuing is the normal method of waiting for your turn in shops, at bus stops and in similar situations. If in doubt as to whether someone is actually in the queue or just standing there, always ask before rushing in. To rush to the front of a queue could cause great offence. CONVERSATION AND LANGUAGE If English is your second or third language, even some people who speak English well may find some local forms of speech or accents difficult to understand. Inferences, sarcasm and inflections of the voice can all alter the meaning of a statement..’ • Do not be worried about saying 'no'. In this country a ‘no’ is not considered impolite. • Honesty is much preferred, so that people know what you really mean. If you do not YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 98
wish to do something do not worry about saying so. ASKING QUESTIONS Never be afraid of asking questions of your host, tutor or lecturer. • Asking questions or putting another point of view is not considered rude in this country. It is often expected that students should have a reasoning, questioning mind, so you will be expected to ask, but don’t take over every conversation by asking too many questions. IMPROVING YOUR ENGLISH The best way of improving English is to use it! Try to find someone with whom you can speak regularly. It is best to talk to people who are not too busy, such as young or retired people. Ask them to tell you if you use a wrong word or if you mispronounce a word. You may also find that the Adult Education Centre in the town run English classes. If you are having problems writing English, you may find that a book helps. There are many good books on written English but if you have difficulty finding one, here are two suggestions: 'The Complete Plain Words'; by Ernest Gowers 'One hundred per cent Report Writing'; by RA Ward WHAT SHOULD I DO IF I CANNOT UNDERSTAND WHAT SOMEONE HAS SAID? • First ask the other person to repeat what they said more slowly, saying, ‘I’m sorry, would you please say that again more slowly?’ • If you still cannot understand, ask for it to be written down. This will help the other person to know that you are having difficulties and may mean that they will take more care to use simple English and speak more slowly. • Do not be worried about letting the other person know that you have not understood: it is not considered rude in the UK to ask a question. WHAT DO I DO IF SOMEONE DOES NOT UNDERSTAND WHAT I HAVE SAID? • You should repeat the comment using different words if possible. • Try writing down your comment – it may be that the other person is not familiar with your pronunciation. YOUTH CULTURE There is no such thing as a typical British young person! People may be identified with one group or another by the clothes they wear and the music they listen to. A friendship group is often very important to them. Britain is no longer a Christian country, and so you may find that many people live in a way you find surprising. BRITISH POLITICS You might just be interested in our politics! Britain has no written constitution, but the system of parliamentary government is the result of gradual change over many centuries. The oldest institution in Britain is the Monarchy, which dates back to at least the 9th century. The British Parliament is one of the oldest representative assemblies in the world. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 99
The House of Lords and the House of Commons both have medieval origins. The British political party system depends upon organised political parties, each of which presents its policies to the electorate. In practice, most candidates in elections belong to either the Conservative Party (Tories), the Labour Party or the Liberal Democrats, although there are smaller parties who stand for Parliament. In recent years, there has been a movement to political decisions being made in the geographical location where they have the greatest impact. The UK now has a devolved government for Scotland and a regional assembly for Wales. Several staff at YWAM Harpenden have read “Watching the English: the Hidden Rules of English Behaviour”, by Kate Fox, and recommend it for more insight.
EATING AND DIET BRITISH DIET Eating habits in the UK have been steadily changing over the last few years, with the introduction of fast food restaurants and other diets. Vegetarian food, pizzas, burgers, Chinese, Indian and other international foods are all now part of the everyday British diet. This means that it is quite difficult to define what ‘British food’ is like! Traditional British dishes normally consist of a meat dish with potatoes and other vegetables such as carrots, peas, broccoli and cabbage. The meat dish is often a type of stew which is meat cooked in a sauce, with vegetables, in the oven. Meat may also be fried, grilled, or roasted in the oven. A sweet dish will normally be served after the main course: dishes such as apple pie (two pastry layers filled with apple), ice-‐cream or cake. Sometimes an extra course called the ‘starter’ or ‘appetiser’ is served before the main course: you might be served something like soup, pâté or melon. Sunday lunch is a great British tradition, and is normally a roast meat dish with vegetables which will be served as the main course. A traditional ‘English breakfast’ consists of cereal followed by fried egg, bacon, sausage and tomato. There will then be served toast and an orange jam known as marmalade. Tea, coffee and orange juice will also be served. However, most British people will usually have a much simpler breakfast of cereal and / or toast with marmalade or jam, with tea, coffee or orange juice to drink. The British mealtimes have various names. This is often very confusing, even for British people – so do ask if you’re not sure! The first meal of the day is normally ‘breakfast’, but sometimes a late breakfast is called ‘brunch’ (combination of breakfast and lunch). A meal is often eaten in the middle of the day, and is usually called ‘lunch’ – this is often light food, such as sandwiches. The evening meal is often the main meal of the day, and it has various names: ‘dinner’, ‘supper’ and ‘tea’ (‘tea’ or ‘high tea’ is more common in northern England and Scotland). ‘Afternoon tea’ is different to the main meal called ‘tea’. Afternoon tea is a light snack type meal eaten in the late afternoon. Traditionally, toasted teacakes (a sweet bread bun with currants and sultanas) or scones (a form of bread dough) are eaten with jam and cream. Often a variety of cakes is served. However, many people understand ‘afternoon tea’ as a cup of tea or coffee together with a cake or biscuit. In some cases afternoon tea can be a more formal affair, especially if you go out for afternoon tea, so feel free to confirm with your host. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 100
The British traditional takeaway meal is ‘fish and chips’. A variety of fish is available (normally cod, haddock or plaice) which is coated with batter and fried in vegetable oil. Batter is made from flour, eggs and milk. Chips are chopped, fried potatoes. Many international takeaways are also available, e.g. Chinese, Indian, Italian, Thai. INTERNATIONAL FOOD Although not every item of your own national food is available in the UK, it is surprising what can be found. • Luton is a very cosmopolitan town which has a large Chinese, South Asian & African population, and so has many specialist food stores. • In Luton and St Albans there are supermarkets which have a wider range of food items. You can find details of the specialist food shops in you’re the area by looking at the ‘Yellow Pages’ telephone directory or the on-‐line version () RESTAURANTS If you go to a restaurant, you will usually be taken to a table by a waiter / waitress. If the restaurant is popular, it is best to telephone and book in advance to ensure that you get a place. Most restaurants serve vegetarian dishes as well as meat dishes. • If you go to a restaurant with a British friend, each person usually pays for their own food, unless your friend has specifically said they will pay. • It is not absolutely necessary but a tip of approx 10% is often left at the end of the meal, except where a service charge is explicitly mentioned on the bill. • If you are leaving a tip, do it in change so that the waiting staff receives the tip. There is a minimum wage in the UK so staff shouldn’t be dependent on tips for a salary. CAFES, TEA SHOPS AND COFFEE SHOPS These are good places to go for a drink (usually non-‐alcoholic, hot and cold drinks). They always have a range of snack foods. In some cafes etc, a waiter/waitress will serve you; in others, you need to go to a counter to order and collect your drink/food.
IF YOU ARE INVITED OUT British people may well invite you out as a sign of friendship and also so that you are not on your own. You should not invite yourself to a meal unless you know the person very well. “WILL YOU COME FOR COFFEE?” People will often use the phrase ‘Will you come for coffee’ to mean, ‘Would you like to come round for a short while and chat.’ Normally different drinks such as tea, drinking chocolate or a soft drink like orange will be available as well as coffee, and you will be asked what you would like. Your host will not normally offer you alcohol at a ‘coffee’ event. • You should accept the invitation the first time if you would like to go. • If you refuse the first invitation, a British person may think this is your final decision and may not ask you again.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 101
ALCOHOL & PUBLIC HOUSES (PUBS) Many British Christians drink alcohol, which may be a real shock to you. A common point of view is: ‘I wouldn’t get drunk. I only drink in moderation.’ Be careful not to seem judgmental of someone who drinks in moderation or tell them it is wrong. • Please read the document in the appendix for guidance from the YWAM Harpenden leadership on alcohol. • If you are asked to go to a public house (pub) you don’t have to drink alcohol. • Soft drinks are available, and often tea and coffee too. • Food is usually a reasonable priced and quality. You usually need to go to the bar to order food and drink – don’t wait for a waiter / waitress to come to you! VISITING PEOPLE’S HOMES It is not normal to ‘just turn up’ at someone’s house. If you need to call to collect something or see someone, write or phone first to arrange a suitable time. An invitation for a meal, or visit to an event or historic site should not be taken as an invitation for an intimate or long-‐ term friendship. DIET Some people may not know what you like to eat so help them as much as possible by explaining the things that you do and do not eat -‐ this will not be considered rude. Tell your host the things you do not eat the week before they prepare a meal for you. ARRIVAL & GIFTS When you arrive, try to be punctual. If you are delayed, a phone to tell your host you will be late. Do not arrive too early either; five minutes early is about right. In most cases (especially when you do not know your host very well) it is usual to take a small gift, such as a box of chocolates or flowers. CAN I BRING MY CHILDREN? If you have children, always ask your hosts in advance whether they are expecting them for the meal or not. If they are invited, you may like to tell your hosts the sorts of food they eat. If your hosts don’t have children, it is helpful to take a book / toy for your child to play with. SEATING & EATING If the meal is served at a table, you should wait until you are called to sit down. The meal will either be served on a plate, or bowls will be passed round from which you help yourself. If there are several knives, forks and spoons at your place at table, always start with the ones furthest away. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 102. WHAT IF I CANNOT EAT THE FOOD? If anything is served that you do not know, feel free to ask, especially if you are vegetarian. If you can't eat anything please tell your host. They will usually understand but remember, mistakes happen, especially if your hosts are not used to having international guests. CLEARING AWAY It is polite to offer the host help to clear away and wash the dishes after the meal, although don’t be surprised if your offer is refused. SHOULD I RETURN THE HOSPITALITY? British people enjoy having guests and will not automatically expect you to invite them back for a meal. Do not feel that you have to invite them. However, if you have a suitable room or flat, and enjoy making a meal, then you will find that a return invitation would normally be welcomed and considered a privilege by your British friends. covers a vast range of subjects related to British life.
HOLIDAYS, SEASONS AND TIME PUBLIC HOLIDAYS The UK has a variety of public holidays when workplaces and offices close for the day. These are often called ‘bank’ holidays. Many shops and facilities close during Day March/April: (dates vary) Good Friday and Easter Monday First Monday in May: May Day Last Monday in May: Spring Bank Holiday Last Monday in August: Bank Holiday 25th December: Christmas Day 26th December: Boxing Day Elsewhere in the UK: 2nd January: Bank Holiday (Scotland only) 17th March: St Patrick's Day (Northern Ireland only) Easter Monday: is NOT a public holiday in Scotland 12th July: Battle of the Boyne (Northern Ireland only) First (not last) Monday in August: Bank Holiday (Scotland only) YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 103
Check the YWAM Harpenden Calendar as there may be more dates for the current year. JOINING IN CELEBRATIONS Many of the local and national celebrations can be very good fun, and it is worth finding out what is happening in your locality. Hogmanay (Scotland’s New Year celebrations) can be particularly lively. At Easter there are often parades and fairs. CHRISTMAS Christmas is a time of year when there are lots of celebrations throughout the UK. However, many facilities in town and on campus may close down between Christmas and New Year. • On Christmas Day and Boxing Day, most shops close and public transport doesn’t operate. • During the weeks before Christmas, churches have special services called ‘Carol Services’, where traditional Christmas songs are sung, often by candlelight. There are always special Christmas services on Christmas Day, but it is worth participating in a hospitality scheme as otherwise you may feel quite lonely during the Christmas period. THE SEASONS AND WEATHER The weather is a favourite topic of conversation in the UK because it changes so much! • Spring (March-‐May) -‐ you can expect pleasant and mild weather; sometimes sunny, sometimes rainy. The north of the UK is generally cooler than the south. • Summer (June-‐August) -‐ warm (average 15-‐20°c / often hotter) and reasonably dry. • Autumn (September -‐ November) -‐ generally mild, but sometimes cold. • Winter (December -‐ February) -‐ cold (average 2-‐5°c) with a combination of rain, snow, wind and fog. You will need a variety of clothing for different times of the year: • It is helpful to have several layers of clothing that can be added or removed as required: wool for warmth, cotton for keeping cool and waterproofs for the rain. • An umbrella is always useful! • A thick pair of gloves, a scarf and some heavy boots (in case of snow) are also very useful, especially if you live in the north of England, Scotland or Northern Ireland. DAYLIGHT HOURS If you arrive in the UK during either June or December, you’ll see that we either have very long or very short days. In 1907, William Willett, a London builder, noticed that summer morning light was wasted while people slept, and that the time would be better utilised in the afternoon by putting the clocks forward. Since 1916 the UK has been changing its clocks backwards and forwards in order to save hours of daylight. • Short days in winter: in mid-‐December the sunrise is at its latest, 08:05* and the earliest sunset is at 15:50*. The shortest day is between 20-‐22 December. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 104
•
Long days in summer: In mid June the sunrise is at its earliest 04:45* and the latest sunset is at 21:20*. The longest day is between 20-‐22 June.
*These times are not exact you can check the exact times through timeanddate.com CHANGING THE TIME We change the time / our clocks and watches twice a year. In the winter months, we have GMT (Greenwich Mean Time) and in the summer it is BST (British Summer Time). Summer time (when the clocks forward one hour) is from the last Sunday in March until the last Sunday in October (when the clocks back by one hour). The change is always made on an early Sunday morning (to minimise disruption) and the exact date is different every year. The date is usually noted in UK diaries and newspapers.
SHOPPING Shopping in Britain is quite easy but you might like to go with a friend the first time in case it all appears a bit strange. The main shopping street in many towns is called the High Street, where you should head if you want to go shopping. Some small shops are owned by local people but most are owned by national 'chains' of stores. This makes many town centres look the same. Some towns have street markets where fresh food and cheap goods can be bought. Away from town centres, small 'corner' shops provide groceries to local customers. WHEN TO SHOP Shops are usually open 09:00-‐17:30 Monday-‐Saturday; in some areas a few shops may close for an afternoon on one of these days, and in cities shops may open later on Thursday evening., ask them for what you want. Although you can use bags that the shops give out, sometimes for a small cost, the trend is to bring your own bags. SUPERMARKETS A supermarket is a good place to start shopping because it is self-‐service and you can walk around and choose the items you want. Many supermarkets supply international foods and often have an information desk where you can get information about what you need to buy. • When you go into a supermarket, always use a trolley or basket for your items. • The main supermarket chains in the UK are: Sainsbury’s, Tesco, Morrison’s and Asda, but you will also find some discount supermarkets called Netto, Lidl and Aldi.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 105
A FEW GUIDELINES If you’re not sure what a good deal is, ask someone to go shopping with you and show you where to get the best product for your price range. Everything should have a price on or near it (e.g. on the shelf) and the law says that the shop has to sell it to you for the lowest price that it is marked. Most big stores use bar codes and scan the items at the checkout. Always get a receipt so that you can change things if there’s a problem..
SHOPPING IN HARPENDEN SUPERMARKETS The largest supermarket in town, Sainsbury’s (on the High St), is within walking distance (20 minutes) of the Oval and offers a wide range of goods. They often say what the price per kg/l etc is so that you can compare the various goods on offer. Sainsbury’s has a range called ‘Basics’ their cheapest range, not always the best but the quality isn’t bad. If you want to look at some of the various costs, take a look at Sainsbury’s have a reward scheme called the Nectar card (‘Boots’, the chemist / pharmacy / drug-‐store also has a rewards scheme which gives more bonuses so it may be better to shop there for certain things). Other local supermarkets are Waitrose and Marks & Spencer. POST OFFICE The main Post Office is on Station Road; as well as postal services, they can often help you in other ways, and offer many other services; PHARMACY Health and beauty products are available from most pharmacies (chemists). The biggest chain is ‘Boots’, which has a shop on the High Street; HOUSEHOLD GOODS For household goods, try Wilkinson (St Albans/Luton) or Ikea (Milton Keynes/ Brent Cross)
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 106
SECOND HAND GOODS CHARITY SHOPS Many charities like ‘Help the Aged’ or ‘Oxfam’ have shops. Goods are donated to the shop, which then sells them to raise money for the charity. It is worth finding out what charity shops there are in your area. They are often a source of good quality second-‐hand goods such as clothes, kitchen utensils, furniture or children’s clothing at very cheap prices. You may be fortunate and find just what you want, so it is worth having a look round each time you go into town. You may spot something that you know you will need in the future! FREECYCLE Freecycle is an internet-‐based community recycling project of re-‐use / sharing usable goods, giving things no longer wanted or needed away for free. It is open to all who want to "recycle" items they no longer need rather than throw them away. Whether it's a chair, a fax machine, a piano or an old door, you can offer it on the group. They have two main rules: Everything must be free. Give before you receive. Keep in mind that Freecycle is not just to acquire things; if you choose to participate, be prepared to be generous, to recycle and offers as many things as you take. There are local networks in St Albans, Luton & Harpenden. EMMAUS Emmaus shops sell a wide range of good quality items at great prices: 2nd-‐hand furniture, household goods and much more. From sofas to sewing machines, books to bicycles, you never know what you might find! Shops in St Albans & Batford:
SHOPPING OUTSIDE OF HARPENDEN St Albans and Luton have good shopping areas; you may also be interested in: HATFIELD GALLERIA: shopping, designer outlets and cinema complex. WELWYN GARDEN CITY: John Lewis Department store: HITCHIN: Has a good market and some good charity shops. WATFORD: HARLEQUIN CENTRE-‐harlequin-‐watford.co.uk/ MILTON KEYNES: THE CENTRE MK mall (and Ikea) BRENT CROSS SHOPPING CENTRE: (including John Lewis + Ikea is nearby)
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 107
MORE TO DO, SEE & KNOW LIBRARIES The Public Library, High Street near Sainsbury's & Boots, contains a wide range of books (fact & fiction), DVDs, newspapers, and magazines. You can also use the internet in some public libraries. You will need a letter from Personnel, stating that you are living at Highfield Oval, to be issued a library card. MUSEUMS Museums contain a wide range of information about local activities, societies and groups, many of which will be available near where you are staying. A local museum is often worth a visit as it will give a lot of the history of the area. Many museums (& art galleries) in the UK are free ( for full list). The National Trust and English Heritage are organisations which maintain many old houses, gardens, castles and areas of land designated as being of outstanding natural beauty. There is often a charge for entry which goes towards upkeep. If you enjoy seeing these sorts of things you will find that membership of the National Trust or English Heritage gives a much reduced entrance fee. TOURIST OFFICES Tourist Offices have a great deal of information about places of interest, historic houses, places to stay and accommodation whilst travelling. They will also given situation. Even if they cannot help you, they will often know who can. The local office can be found from the telephone directory or on the Citizens Advice website. POLICE The police are well respected in the UK and will be very pleased to help you if they can. Apart from dealing with law and order issues, it is always worth going into your local police station if you lose anything while you are out as lost property is often handed in to the local police station. • If you come across an accident, it is always worth contacting the police. • You should also report any crimes at your local police station, for example if someone steals something from you. IF YOU ARE DISABLED If you are disabled in any way, or have special needs, talk to your team leader about how they may be able to help you. If you want to travel locally or nationally whilst you are in the UK then, depending on your needs, there are several organisations that may be able to help. • Contact the Royal Association for Disability and Rehabilitation for more information: Phone: 020 7250 3222 • email: radar@radar.org.uk • Web Site: YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 108
ENTERTAINMENT You will be able to find cinemas, theatres, dance venues, and informative lectures in your area. Remember that some films and plays may contain violence, language, or sex scenes which you may find objectionable. See the British Board of Film Classification's rating of films as a guide to content (bbfc.co.uk). CINEMA The nearest cinema is Luton Cineworld; plus Ten Pin bowling in the same building. Cheap nights are on Tuesdays and if you have a mobile phone with Orange, you can sign up for “Orange Wednesday’s” for a deal that gives you 2 for the price of 1 on movies & meals at Pizza Express. Check with Orange.co.uk for more information. TELEVISION The UK's five most watched channels are BBC One, BBC Two, ITV, Channel 4 and Channel 5. The watershed on standard television in the UK starts at 21:00 and finishes at 05:30 the next morning. Programmes rated 15 cannot be shown outside this period. However, some 12-‐rated shows can be shown before 21:00. TELEVISION LICENCE In the United Kingdom, any household watching or recording live television must purchase a television licence every year (until 2016, £145.50 for colour; £49.00 for black and white). The licence is required to receive any live television transmission, whether it is received via terrestrial, satellite, cable, or the Internet. A licence is not, and never has been, required simply to possess a TV set, for the purpose of watching pre-‐recorded content, or use as a monitor for video games or computers. Although income from the licence is primarily used to fund the television, radio and online services of the BBC (they do not have any advertising to generate income), a licence is needed to view all broadcast channels, including commercial services. If you watch television via one of the five main channels online you do not require a licence if you are not watching live. ICE-RINK The nearest ice-‐rink is at Hemel Hempsted.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 109
APPENDIX
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 110
REVIEW DATES My start date at YWAM Harpenden is: I will have been at YWAM Harpenden for 3 months: My 3 month review date is: My team is: My team leaders are:
________________________________ ________________________________
________________________________
________________________________
________________________________
TO DO LIST:
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 111
GUIDELINES ON DRINKING ALCOHOL AT YWAM HARPENDEN In common with YWAM bases around the world, Highfield Oval welcomes staff and students from many nations and peoples of the world. We enjoy and celebrate the cultural diversity we find within the mission. Within the norms of Biblical standards we seek to accommodate one another, in Christian love, rather than trying to impose a particular standard or set of expectations on our individual behaviour. At the same time we need to be careful not to offend one another or to cause anyone to slip in their own standard of behaviour. Inevitably we will find a variety of legitimately held views within the Oval at any particular time over a number of issues, not the least of which will be the attitude to the consumption of alcohol. In view of the variety of opinion on the issue we offer the following policy framework to allow freedom of expression and an environment in which individuals can be true to their standards and beliefs on this matter. A strict no alcohol policy operates in all student accommodation and public places on Highfield Oval. Alcohol may neither be consumed nor taken into these parts of the premises. Exceptions can be made with the permission of the Leadership Team for events such as wedding receptions. Please check with the Leadership Team first. Students may consume alcohol socially off the premises in restaurants, private homes, or public houses with discretion, and in moderation. However, frequent drinking is definitely discouraged and is a matter of accountability for discipleship; inebriation, even to a mild extent, is not permitted and will lead to the student being asked to leave at the first offence. Mild inebriation includes slurring of speech, staggering, and hangovers. There will be times when the consumption of alcohol will be expressly forbidden by school leaders, such as on outreach to countries where the cultural norms of Christianity do not allow it, to Islamic states, or where the leaders are aware of a particular student having a past history of difficulty in the use of alcohol. Students are also reminded of the fact that amongst their number may well be those who have struggled with alcohol or other substance abuse in the past and are requested to be sensitive in suggesting outings as well as in their own behaviour. Staff at the Oval may consume alcohol in similar circumstances to those outlined above for students, off site, and may drink alcohol within self-‐contained accommodation. Staff should exercise discretion and wisdom at all times, bearing in mind the sensibilities of other cultures and traditions as well as those amongst us who may be recovering alcoholics. When alcohol consumption becomes a regular feature of life, even if not to excess, staff may be asked to hold themselves accountable for their activities. Becoming drunk is a disciplinary issue within the community.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 112
SMOKING We recognise that smoking can be a symptom of deeper issues, emotional and / or spiritual, that will-‐power alone cannot overcome. We have no desire to shame or ostracise anyone wrestling with addiction, rather, we are committed to helping any staff member deal with the root causes through ongoing prayer, discipleship and accountability. However, All YWAM Harpenden staff should refrain from smoking, including cigars & hookah. We welcome visitors from diverse cultures and backgrounds, with different views on many issues; please remind them that smoking is not permitted in any of our buildings.
SUBSTANCE / DRUG ABUSE Under no circumstances are any staff members or trainees permitted to indulge in the recreational use of illicit substances / drugs. Such behaviour will result in the offender being asked to leave at the earliest opportunity and seek professional help. For more understanding or to discuss any of these things, please see a member of the Leadership Team or Personnel Team.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 113
FIDELITY: KEEPING COMMITMENTS (Updated October 2009) Fidelity is a word that includes loyalty and faithfulness. It is rooted in the character of God who is always faithful, who always keeps his commitment to us and promises to be with us forever. However, we live in a world where commitments, even marriage vows, are constantly being broken. That brokenness affects us all. From time to time staff members make a commitment to a team or ministry here at YWAM Harpenden, and then fail to see that commitment through. When we find ourselves in the position where someone on our team comes to us with ‘guidance’ or a decision that they should leave before completing their commitment, we often don’t know how best to respond. We always hesitate to over-‐rule “guidance” and we are also hesitant to persuade someone to stay when their heart is not in it. We want to avoid these situations. They are difficult for all involved, but we are aware that it reflects that we have not discipled people well and that we have failed as teams and leaders. We would be less likely to find ourselves in this situation if the commitment process is clearer, more formal, serious and celebratory. We would like to record and celebrate commitments in a more public way, rather than it just being a line on an staff application. It is helpful to understand that most people experience doubts, discouragements and tears at some points after the “honeymoon” of a new commitment. Our understanding is that when we have discerned God’s leading and made a commitment, it is not something that is simply changed by new “guidance.” In fact, God’s Word is very strong on us keeping our commitments, even when we have made rash ones. Potential new staff should never be pressured to make a commitment they are not freely choosing and they should never have that commitment accepted until they have realized that it is a serious vow. It is a commitment made in obedience to how God has led them. We need to be reminded of the scripture “When you make a vow to God, do not delay in fulfilling it. He has no pleasure in fools; fulfil your vow. It is better not to vow than to make a vow and not fulfil it. Do not let your mouth lead you into sin.” (Ecclesiastes 5:4-‐6) This holds true for leaders and team leaders as well. Sometimes leaders recruit staff enthusiastically and then move on quickly. Occasionally this can’t be avoided, but as leaders, team leaders and community members it is very important to keep our commitments to one another with fidelity. If some major change in life occurs, such as the death of a very close family member or an illness that requires their assistance at home etc., we will, of course, reconsider the terms of a commitment. But we will not readily receive news of different “guidance.” We believe this is an important part of our calling to make disciples. Fidelity and faithfulness are central to following Jesus. When we easily change solemn commitments we have made, we are not helping one another to live in the fear of the Lord who commands us to “Let your 'yes' be yes, and your ‘no’ be no!” (Matthew 5:37)
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 114
NOTES FOR REGISTRATION WITH THE INLAND REVENUE FOR INCOME TAX & NATIONAL INSURANCE This document does not constitute financial advice and is subject to errors and omissions. Remember it is your responsibility to register with HMRC , keep accurate records and submit a yearly tax return (if required) as well as registering for National Insurance . Compiled by Anne Sloan, National Support Team, September 2010; revised May 14th, 2012. SUMMARY PAGE 1. All those who wish to volunteer with Youth With a Mission (YWAM) England & Wales on a full time basis need to register with the Inland Revenue (IR) as self-‐ employed missionaries. If you live in the UK for more than 183 days of a tax year (6th April to 5th April) you are liable to pay UK Income Tax. 2. You need to register with Her Majesty’s Revenue & Customs (HMRC). The online website is or phone the helpline on 0845 9154515, or use the wording provided as a template at the end of this document. 3. As a full time volunteer with YWAM England & Wales, you are classed as being self-‐ employed and you are responsible for paying your own tax and National Insurance contributions. 4. You need to keep business records and details of your income so you can fill in an annual Self Assessment tax return. 5. If you don't do this you are liable for penalty fines-‐you need to register within 3 months of starting with YWAM-‐the initial fine is 100 pounds for not doing this, which can increase by up to 10 pounds per day. It is your responsibility to register and complete self-‐assessment forms, YWAM cannot do it for you. 6. Each year you are entitled to a personal allowance that means you can receive a certain level of income without paying tax. It may well be that you do not need to pay any income tax, but you MUST register with the HMRC nonetheless (April 2012 – April, 2013 the tax allowance has increased to £8,105 for under 65 year olds). For the tax year 6th April 2013-‐5th April 2014 the allowance will be increased to 9,440 pounds. 7. You must also register for National Insurance. As full-‐ time volunteers with YWAM England & Wales you are entitled to pay the self-‐employed National Insurance contributions which are very reasonable. However if you earn less than a certain amount you can apply for a small-‐earnings exemption certificate.. 8. If you have any questions, you can contact the HMRC helpline (who are very helpful) or the Personnel Department for general enquiries. GUIDANCE NOTES • All those who wish to volunteer with Youth With a Mission (YWAM) England & Wales on a full time basis need to register with the Inland Revenue as self-‐employed missionaries. This is a legal requirement and if you do not do this you are liable for a penalty fine. You are responsible as an individual for doing this and it is not the responsibility of YWAM. You need to do this within 3 months of starting with YWAM otherwise you are liable for a 100 pound fine (which may increase). YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 115
•
•
• •
All UK subjects and non-‐UK subjects who live in the UK for more than 183 days of a tax year (6th April to 5th April) are liable to pay UK Income Tax. You need to register with Her Majesty’s Revenue & Customs (HMRC). The online website is easy to navigate and has all the information you need. Register online or phone the newly self-‐employed helpline on 0845 9154515. It used to be the case that you would contact your local HMRC office, but now when you write or phone you will be allocated to the nearest HMRC office that is available – this could be anywhere across the country, but once you are registered they will be able to access all your information whenever you contact them. Please do not hesitate to contact them with any questions or concerns, they are very helpful and willing to steer you through their procedures and systems.
INFORMATION FROM THE HMRC WEBSITE SELF-‐EMPLOYED TAX AND NATIONAL INSURANCE If you're self-‐employed, you are responsible for paying your own tax and National Insurance contributions. You'll need to keep business records and details of your income so you can fill in an annual Self Assessment tax return. The website () has more detail on: • Register with HM Revenue & Customs (HMRC) • Income Tax and Self Assessment • National Insurance contributions • Record keeping • More useful links INCOME TAX AND SELF ASSESSMENT Once you're registered as self-‐employed,.. Please go to the website () for more information on: • Levels of Personal Allowance • How do you get the Personal Allowance? • Who can't get the Personal Allowance? • Other allowances you may be able to get • Giving to charity -‐ effect on your allowances • More useful links
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 116
Levels of Personal Allowance • The amount of Personal Allowance depends on your age + your income in the tax year • Total income means everything you receive from all taxable sources. That means you need to include things like pensions and interest on your savings in a building society before the tax has been taken off. There are three levels of Personal Allowance If you become 65 or 75 during the year to 5 April 2013, you are entitled to the full allowance for that age group (see for current rates) Personal 2012-‐2013 tax year 2013-‐14 tax year Allowance Basic
£8,105
9,440 pounds
Age 65-‐74
£10,500
10,500 pounds
Age 75 and over £10,660 10,660 pounds NATIONAL INSURANCE CONTRIBUTIONS You normally have to pay Class 2 National Insurance contributions and if your annual profits are over a certain amount you also pay Class 4 contributions. Class 2 National Insurance contributions Class 2 National Insurance contributions are a flat rate of £2.70 a week. If earnings are below £5,725 per year (2013-‐14) you may not need to pay ( Class 2 contributions count towards certain benefits, like the basic State Pension, Maternity Leave and Bereavement Benefit, but they do not count towards the additional State Pension, Statutory Sick Pay or Jobseeker's Allowance, so you might want to think about making other arrangements like a personal pension and income protection insurance. EXCEPTIONS TO PAYING CLASS 2 NATIONAL INSURANCE CONTRIBUTIONS If you earn less than £5,595 per year you can apply for a certificate of small earnings exception and not pay Class 2 National Insurance contributions. However, you might decide to carry on paying them voluntarily to keep your entitlement to the State Pension and other benefits. As at Sept 2010 you need 30 years of National Insurance Contributions to qualify for a full state pension. However this could change in the future. (and I have heard that it will probably go up to 35 years soon-‐until recently it was 40 years-‐Anne). For married women you can get 60% of your husband’s state pension if you do not have your own. RECORD KEEPING Legally you have to keep records for your business and for any other income. This is so you can fill in your tax return and show that the figures are right. You need to keep at least: • Invoices for sales and purchases • Receipts for business expenses • Bank records YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 117
Good records will also save you time and help you run your business more efficiently. Find out about Self Assessment record keeping:- emp.htm (End of information from HMRC website) GUIDANCE NOTES: HOW YWAMERS RECEIVE SUPPORT (INCOME) Gifts to Staff Members YWAM staff do not receive salaries but are responsible for raising their own support. For most YWAMers this includes from family, friends and supporting churches. Each person is responsible to set their own financial budget. YWAM believes that this kind of personal support creates a healthy situation between the staff member and the giver because: • The YWAM worker is directly accountable to their supporters through personal relationships. • It creates a support team for the YWAM worker which includes prayer, accountability, friendship and encouragement as well as financial support. • It allows supporting churches and individuals to be personally involved in the mission and ministry of the person whom they support. This is how gifts to YWAM workers may be given: • By payment directly to the individual (regular or one-‐off gifts) • By standing order into the worker’s bank account • Stewardship (incorporating UKET and Sovereign Giving) and SKI. Full time Christian workers can receive gifts on which the tax paid can be recovered, thus increasing the value of the gift by 25% (the giver needs to be a UK taxpayer, the recipient can be a non-‐UK subject but must have a UK bank account). We recently received clarification from Stewardship Services as to restrictions on gifts where the tax can be recovered. This is their statement: • “To confirm, as a full time Christian worker donation requests from close relatives (or spouses of) may only be used for Ministry Expenses, we also need to have confirmation in writing of that understanding from the donor. Close relatives are as follows: Grandparents, Parents, Siblings, Children, Grandchildren (or spouses of). If you are studying and not in ministry no donations may be made by any of the above. There are no restrictions on friends supporting individuals”. Giving Services Engagement Team, Stewardship. 24th January, 2011. See and for further details. WHAT IS TAXABLE INCOME?
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 118
The general rule is that any income received by virtue of your vocation is taxable, irrespective of who gives it to you. YWAM used to have a blanket agreement with HMRC until 2005 when all blanket agreements were cancelled. However, our agreement was not cancelled because it was unreasonable, but because HMRC no longer has blanket agreements. It is suggested that when you register you agree with the HMRC directly which income you receive needs to be declared as taxable income. Alternatively, ask your accountant to do this on your behalf. Taxable Income 1. Gifts from churches to a YWAMer, even if you haven’t carried out any work for them. 2. Gifts from churches to YWAM to cover staff fees of a YWAMer. 3. Gifts from trusts (i.e. SKI, Stewardship, CAF) 4. Honoraria received in return for performing duty (i.e. speaking in a DTS, church) 5. Reimbursements from YWAM for travel 6. Gifts from friends. Under the old blanket agreement the HMRC agreed to allow gifts from friends to be taxable at 50% (i.e. if you received £100, £50 would be taxable and £50 would be non-‐taxable). However this agreement is no longer valid. Under BIM62101 – Missionaries and evangelists: Income from vocation the HMRC state: that personal gifts from parents or immediate friends are not considered taxable receipts. This may need defining with HMRC but at the very least you must keep records of all income, including donor, date and reason for gift. 7. Bank interest, dividends, rental income etc. NON-‐TAXABLE INCOME 1. Gifts from parents 2. Gifts from immediate friends (see above) 3. Personal testimonials, or personal gifts, for example on marriage or for medical treatment. It has been understood in the past that regular gifts from friends that are given to assist you being a missionary are taxable but a one off gift for a specific purpose is not. However, it is your responsibility to establish this with HMRC directly (or via an accountant). BUSINESS EXPENSES You can make deductions from your taxable income to reduce your tax liability. You can deduct any expenses which are incurred wholly and exclusively for the purpose of your work. In practice if an expense is incurred partly for business and partly for private purposes, then HMRC will allow you to claim a percentage of the expense as a deduction. Here are some examples of business expenses 1. Travel expenses (but not to and from permanent place of work) 2. Outreach expenses 3. Telephone, stationary, photocopy, stamps YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 119
4. Research material 5. Support raising costs 6. Office at home, you can deduct a percentage of the costs for rent, light heat, water 7. Conference fees 8. Further training schools/courses 9. Accountant’s fees 10. Professional subscriptions 11. Any business assets under £200 12. Assets over £200 * 13. Vehicle expenses ** * If an asset costs more than £200 you can deduct 25% of the cost per year on a reducing balance basis. This deduction requires some special calculations and a schedule is available in the HMRC personal tax forms. See example below. EXAMPLE: Computer bought for £781.74 Year 1 Original Cost £781.74 @25% £195.43 (this would be the amount of deduction) Carry forward £586.31 (£781.74 minus £195.43) Year 2 @ 25% £146.58 (this would be the amount of deduction which is Carry forward £439.73 25% of the carry forward of £586.31) Year 3 @ 25% £ 109.93 (this would be the amount of deduction) Carry forward £329.80 Year 4 @ 25% £82.45 (this would be the final deduction at year 4) ** You can deduct a percentage of your personal vehicle operating costs if you use your vehicle for business. These costs would include petrol, insurance, road tax and repairs. The amount you can deduct is based on the proportionate amount of time you use your car for business or personal use. If you drive 10,000 miles per year and 6,000 are related to business then you can deduct 60% of your car expenses per year. The actual cost of the vehicle can also be deducted from your taxable income on the same 25% basis as for other assets, subject to a maximum of £3,000 per year. Alternatively, you can claim mileage (only mileage exclusively for business) at a rate of 45p a mile (up to 10,000 miles) then 25p a mile thereafter. Accurate records will need to be kept of all your car usage and mileage. RECEIVING INCOME FROM ABROAD? For those of you who receive income from abroad you will need to give details to the HMRC. The important point is that you register with them and they will advise what taxable and non-‐taxable income is. There is a section in the annual tax return to declare foreign income. WHEN MUST A TAX RETURN BE SUBMITTED BY? If you file a paper tax return it needs to be submitted by 31st October i.e. the tax return for the year 2012 – 2013 needs to be submitted by 31st October, 2013. If you file an online tax return you have until 31st January, 2014 to file. If you miss this deadline there is an automatic penalty of £100 (except for a few exceptional cases see the HMRC website). When is tax payable? If you are due to pay income tax you will pay in two instalments, one due on account by 31st July and the balance due by 31st January. The one due in July is usually paid in advance for YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 120
the current tax year. As you do not know what your exact income is until you complete your tax return after the year-‐end, then the balance is due by the end of January (or if necessary a refund will be made). You can pay any monies due by cheque or via your bank account. Penalties and interest There is a fixed penalty for not submitting your tax return on time of £100 each deadline you miss. There are also interest payments to be made for late or incorrect payment of tax. YOU HAVE BEEN WARNED! What do I need to do next? 1. Decide whether to use an accountant or to do the work yourself 2. Complete form CWF1 – notification of self-‐employment from the Inland Revenue – you must register within 3 months of your start date 3. Keep records of all expenditure and all gifts/income. You need to keep records for a minimum of 7 years 4. Keep copies of all correspondence with HMRC 5. Submit a tax return each year (unless HMRC inform that you no longer need to) 6. If you have any questions, please see your personnel department. This document does not constitute financial or legal advice and is subject to errors and omissions. Remember it is your responsibility to register with HMRC, keep accurate records and submit a yearly tax return as well as registering for National Insurance. Compiled by Anne Sloan, September 2010; revised May 14th, 2012 & April 2013
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 121
Sample Letter to send to HMRC for registering for National Insurance & as being self-employed HM Revenue & Customs Date Dear Sirs Your name NI number-‐if you already have one I have recently commenced voluntary mission work with Youth With A Mission (YWAM), a Christian charity that is based in (put in your location where you will be mainly based). My work with them is unpaid and I have to organize my own funding. This funding will arise from a number of sources amongst which will be: My home church My family Friends Speaking engagements Some of this income may be paid through charitable trusts which collect gifts for me under Gift Aid arrangements. I understand from YWAM that I must organise my own tax & National Insurance affairs and that for tax purposes I am considered to be self-‐employed. With this in mind I shall be most grateful if you will provide me with form CWF1 so that I may register with you as self-‐ employed for both income taxes and National Insurance purposes. I look forward to hearing from you shortly, and thanks for your help. Yours faithfully
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 122
PROCEDURES FOR OVAL SECURITY CHECK Thank you for participating in the Oval Security Check. As residents, we rely on the Lord for our corporate safety and the safety of our facilities. However, we have a part to play in that, and your participation in the nightly security check makes a real difference and helps prevent and stop crime! Here are guidelines and instructions to make us consistent in our security checks. Please take note of these points and perhaps connect them to the reminder you put on your calendar for the week you are signed up to serve. The rota for this job is on the Intranet, listed as “Security Check Rota”. When do I do this? Note on your calendar the week you are on the security rota. If it turns out that you can’t do it, please swap with someone and note the change. Your week begins on the Sunday night and ends the following Saturday night. Please do your round at 22:30. It should take no more than half an hour. You will receive a high-‐visibility jacket, torch, and front gate key from the security patrolman who does security the week before you. More jackets are available from Peter Kinahan. What do I do on my rounds? Walk around the main residential and office buildings and around the Factory, checking for the following: Ground floor windows should be shut and locked. Exterior doors should be shut and locked. Pay particular attention to the rear of the Bramley Building and the Factory. The presence of anyone not here as staff, student or invited guest (see below for what to do in case you find any!) Lock the front Oval gate. You should receive the key from the previous security guard. There is a spare in reception. Note: There is no need to check doors which open directly into a private residence (e.g. the bungalows, #1, flats which have exterior doors which open directly into a flat) unless they are known to be unoccupied. You don’t want to accidentally walk into somebody’s house or scare them by appearing to be breaking in! What do I do if I encounter someone who should not be here? If they do not appear threatening, and you feel comfortable doing so, approach and, unless they have legitimate business here, ask them to leave as the site closes to the public at 20:00 (as posted on the signs). Evangelism is effective as a means for handling belligerent visitors. They get saved or they leave!
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 123
If the person appears drunk or is behaving in a suspicious manner, and in any case where there is more than one person, you should never approach alone. Call another male staff member(s) for backup. In the case of criminal activity (vandalism, underage drinking, unlawful trespass, etc) ring the police immediately on 999 and say you want to report an incident of whatever the crime is in progress at Highfield Oval, on Ambrose Lane, Harpenden. Use your cell phone to take photos! Call a member of the Leadership Team. Note any unusual vehicular activity and registration numbers in particular. These details can be added to the Intranet on the Security Check Rota entry for the week you are on. There is a space there for “Information”. Contact Oval Operations with any concerns or incidents and also pass the information on to the following week's security person. Doors / windows that simply do not close should be mentioned. Thanks very much for serving in this way!!!
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 124
Holiday & Time Away Request Form
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 125
YWAM HARPENDEN FACILITIES REQUEST FORM
Please read the details on FACILITIES BOOKING in the HOOT section of the STAFF When complete scan and email bookings@oval.com or hoot@oval.com
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 126
LOCAL SCHOOLS AND HOW TO APPLY A GENERAL OVERVIEW The school year begins on 1 September. Education is compulsory for all children from their 5th birthday to the last Friday in June of the school year in which they turn 16. State-‐funded nursery education is available from the age of 3, for up to 15 hours a week. If registered with a state school, attendance is compulsory beginning with the term following the child’s fifth age 16. SCHOOL YEARS The table below describes the most common pattern of schooling in England: Age on Aug 31 Year Curriculum Stage Schools 3 Nursery Foundation Nursery School 4 Reception Stage Infant School 5 Year 1 Key Stage 1 6 Year 2 7 Year 3 Key Stage 2 Junior School 8 Year 4 9 Year 5 10 Year 6 11 Year 7 Key Stage 3 Secondary 12 Year 8 School 13 Year 9 14 Year 10 Key Stage 4/ GCSE 15 Year 11 16 Year 12 Sixth Form / A level Sixth Form college 17 Year 13
Primary School
Secondary school with sixth form
USEFUL LINKS Hertfordshire County Council School Admissions including appeals process School Term Dates Nursery Admissions Primary School Admissions Secondary School Admissions YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 127
INFORMATION ON LOCAL SCHOOLS This is not an exhaustive list, but is a list of schools that children living on the Oval attend. To find out more, go to where you can read school inspection reports. However, your most reliable source may be talking with other families on the Oval that have children to these schools and asking their opinion. PRESCHOOLS Highfield Preschool The Lea Nursery-‐pri.herts.sch.uk/ PRIMARY SCHOOLS The Lea Nursery and Primary School-‐pri.herts.sch.uk/ Manland Primary School Roundwood Primary School SECONDARY SCHOOLS St Georges Roundwood Park Sir John Lawes
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 128
DEPARTING YWAM HARPENDEN - A CHECKLIST Before you leave Highfield Oval, many practical details need to be sorted. Therefore, please ensure that you have dealt with every task listed and give yourself enough time to do it before you leave. Our desire is to also have time to pray for you at a staff meeting before you go, so please arrange this with the Leadership Team / Personnel. A ‘Farewell Celebration’ is the responsibility of your Team Leader to arrange and publicise. Emails to send: • personnel@ywamharpenden.org -‐ to let us know your date of departure • dg.everyone@oval.com -‐ to inform us all of your departure and plans for the future • accounts@oval.com, helpdesk@oval.com & housing@oval.com with your date of departure -‐ so that they can work out your final rent, phone lines & Internet • Please set up an ‘Out of Office’ reply to your ywamharpenden.org emails. IT may be able to help you with this. Meetings to schedule: • Make sure that you have a closure / de-‐briefing time with your Team Leader • Accounts Dept: make sure all bills are paid (Rent; Vehicles; Phone; Internet; BB Hall food: Please make sure you have crossed your name off the BB Hall list). • If you pay council tax directly to the district council, please contact the council but give Personnel a copy of any letter before you send it to the Council. Quite often, if you are paying in ten monthly instalments, the Council may give you a refund • GP: Please inform your doctor’s surgery that you are leaving. Important! • Dentist: Same as GP. • Library: inform them you are leaving and ensure you have no books still out on loan. • Bank Account -‐ Please either close it or give them your change of address. Your bank statements will only be forwarded to you for a couple of months, not indefinitely. • TV Licence – Please inform the TV Licensing Authority of your change of address if you have a TV in your flat / room. • Self-‐Employed Tax Dept – Please inform the Inland Revenue about your change of address for your self-‐employment status to be correct. • Room/Flat -‐ cleaned & signed off by the Housing team (see ROOM/HOUSE CLEANING CHECKLIST). • Keys returned: Please return your flat/room keys to personnel. • Take personal possessions with you or dispose of them yourself! • Return borrowed furniture in your accommodation to the owner. • Return any office keys in your possession. • Forwarding Address: Please give this to Personnel, as well as writing it on this paper. Also, please state who, if you have asked anyone to be responsible for your post. • Personnel will forward your post for six weeks: After that we will ‘return to sender.’ • If you’re here on a VISA: please give your flight and departure details to Personnel.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 129
ROOM /HOUSE CHECK OUT FORM ** Please ensure you have done all of the following in cleaning your room/flat *** Check with housing@ywamharpenden.com if in any doubt as to what you need to do! • Returned the room / flat paintwork to ‘neutral’ (white/off-‐white). • Removed all personal possessions (disposed of them or taken them with you). • Washed your radiators with a damp cloth on the outside, inside and underneath. • Damp-‐wiped all shelves, and cleaned wardrobes, chests of drawers, bedside tables, and other cupboards inside and out. • When done, arrange with housing to inspect your room quickly before it gets dirty again. Ask them to bring you a cup of tea when they come, as you jolly well need it! Windows: • Cleaned on the inside. • If you have been here for 3 months or longer, clean the windows on the outside too, either yourself or pay for a window cleaner. (DP Windows – 07837 278662 or KEKS -‐ 01582 622695 are reasonable and have been used by others on the Oval) • Any mildew/mould cleaned from window frames. Walls & Ceilings: • Washed down all paintwork (skirting boards, door frames, window frames) • Any and all marks on walls should be cleaned. • Removed all nails or picture hanging hooks and fill in the holes • Wiped away all cobwebs in the corners of your ceilings, on the light fixtures or anywhere else you may see them. Floors and Carpets: • Moved all furniture to vacuum and / or mop beneath everything. • If you have been in the room more than 1 year, clean (shampoo) the carpet. Bathroom: • Cleaned the toilet, sink and bath/shower of all stains. • Removed any lime scale with either white vinegar or lime scale remover. Kitchen: • Washed & cleaned the tops and inside the drawers of all cupboards & shelves with an anti-‐bacterial cleaner. • Freezer/fridge: Emptied & cleaned-‐out and deep cleaned / de-‐frosted. Moved and cleaned the floor underneath. Afterwards, plug back in with the door closed, or leave unplugged but with the door open so it won’t close, as this makes it smell. • Cooker: cleaned thoroughly -‐ top, sides, grill, hob and oven. Move it and clean the floor underneath. • Kitchen sink: cleaned thoroughly, again all lime scale stains removed. For any outstanding maintenance problems, such as dripping taps, leaking roof, etc.... Please indicate if you have contacted maintenance already. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 130
YWAM England Safeguarding Procedure SAFEGUARDING GUIDELINES FOR All YWAM ENGLAND STAFF AND TRAINEES If a child or vulnerable adult makes a disclosure -‐ or if you suspect a child abuse related issue: 1. LISTEN, LISTEN, LISTEN! comfort and reassure child or vulnerable adult; listen carefully; only ask questions to clarify what has been disclosed, not to delve and explore; do not promise confidentiality; encourage them that they did the right thing in sharing with you; 2. Make sure they are safe. And consider others who may also be at risk. 3. Contact the first available person on this list: Your Base or Team or Ministry Leader. If suspicions/allegations involve this leader, contact ST directly. Safeguarding Team (ST) If suspicion/allegation involves some one on the ST, contact another person on ST or contact CCPAS directly. Churches Child Protection Advisory Service (CCPAS) If a report is made to the CCPAS first you should contact the nominated ST within one working day. Local Children’s or Adult Services, as appropriate. 4. Do not discuss with any other person, except police or social services if approached by them. THIS INCLUDES PARENTS/CARERS! 5. Make dated notes of everything said, as well as person’s name, DOB, address. Do not expect a continual update of incident -‐ only a reassurance that it is under control and being monitored.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 131
YWAM England Safeguarding Team and Other Important Contact Numbers (List to be updated as necessary) Please fill in telephone numbers for your location Safeguarding Team Rob Hobbs 07734 440594 Serena Baker 07795 844473 Steve Bishop: 07825 767696 Anne Sloan: 07905 419120 Helena Kittle: 07860 138087
Base/Team Leader________________ Mobile_________________ Churches Child Protection Advisory Service (CCPAS) 0845 120 4550
Local Children’s Services Phone Number ______________________________ Out of hours number ______________________________________________ Local Adult Services Phone Number __________________________________ Our of hours number ______________________________________________ Local Police Phone Number _________________________________________ In an urgent emergency, ring 999. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 132
YWAM ENGLAND SAFEGUARDING POLICY PROTECTING YOUNG PEOPLE AND VULNERABLE ADULTS AND APPOINTING WORKERS
1. INTRODUCTION Youth With A Mission (England & Wales) Ltd. (Registered Office: Highfield Oval, Harpenden, Herts., AL5 4BX, UK. Reg. Charity No. 264078. Company Registration No. 1049516 in England and Wales. Member of Evangelical Alliance and Global Connections.)
Public Liability Insurance held with Ecclesiastical Insurance Office plc. Local YWAM Team/Base Address and Contact Details: _____________________________________ __________________________________________________________________________________ __________________________________________________________________________________ YWAM has a long tradition of working with children, young people, families and vulnerable adults. We take seriously our responsibility to protect and safeguard the welfare of children, young people and vulnerable adults throughout their association with us.. As part of our mission we are committed to: listen to, respect and value children, young people and vulnerable adults whilst ensuring their protection within our activities; adopting a procedure for dealing with concerns about possible abuse, and reviewing and revising this procedure regularly as needed; encouraging and supporting parents/carers; safe recruitment, supervision and training for all YWAM workers appropriate to their level of involvement with young people and vulnerable adults. (For the purposes of this policy, “workers” includes all staff, trainees, volunteers, mission builders and associates); maintaining good and constructive links with the statutory childcare authorities and agencies working with vulnerable adults; endorsing and following all national and local safeguarding legislation and procedures, in addition to the international conventions outlined above;
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 133
working toward ensuring that our premises meet the requirements of the Disability Discrimination Act of 1995; supporting the Safeguarding Team in their work and in any action they may need to take in order to protect children and vulnerable adults; file a copy of the policy and practice guidelines with CCPAS and the local authority ______________________________________ [LSCB, Social Services etc please state here where your team/base have lodged your policy], and any amendments subsequently published; supporting those affected by abuse in YWAM. YWAM recognises that many children, young people and vulnerable adults today are the victims of neglect and physical, sexual, emotional and spiritual abuse. Accordingly, we have adopted the policy contained in this document entitled: Protecting Young People and Vulnerable Adults and Appointing Workers (hereafter the policy) .The policy sets out agreed guidelines relating to the following areas: responding to allegations of abuse or neglect, including those made against leaders or members of YWAM. appointing workers, whether or not they work directly with young people or vulnerable adults, recognising that within YWAM, workers roles vary frequently over time, thus opening the possibility of direct involvement. Also community lifestyle and values require care towards one another. supervision of activities, and practice issues. YWAM recognises the need to build constructive links with the child care agencies and agencies working with vulnerable adults. Accordingly these guidelines have been based on the ten “Safe and Secure” safeguarding standards from the Churches Child Protection Advisory Service (CCPAS). The content of this policy will form the basis of a training programme for all workers in the organisation. YWAM is committed to an ongoing training programme for all workers. The policy contained here is formulated to help YWAM workers to: create and maintain a safe environment for young people and vulnerable adults. respond appropriately to concerns, allegations and disclosure of abuse. Nothing in this policy absolves or detracts from a YWAM parent’s personal responsibility for the care and protection of young people in any private arrangement made with workers, for example baby-‐sitting, childminding, private outings and other privately arranged activities. Where arrangements are made to provide child minding, those undertaking these arrangements need to be mindful of day care legislation e.g. the childminder needs to be registered with social services etc. Parents/those undertaking parental responsibility should be aware of day care standards. The DofEE have produced a booklet on finding a child minder. This policy will follow legal guidelines that a child is anyone under the age of 18. And this policy will follow the definition given in No secrets: Guidance on developing and implementing multi-‐agency policies and procedures to protect vulnerable adults from abuse’ -‐-‐ Department of Health and Home Office (March 2000) -‐-‐ which states that a vulnerable person is someone: ‘who is or may be in need of community care services by reason of mental or other disability, age or illness; and who is or may be unable to take care of him or herself, or unable to protect him or herself against significant harm or exploitation’.
2. RECOGNISING AND RESPONDING APPROPRIATELY TO AN ALLEGATION OR SUSPICION OF ABUSE Abuse is a very emotive topic about which people have a wide range of attitudes and feelings. People often get very upset and angry when considering the area of abuse, particularly in relation to sexual abuse. If YWAM workers are to deal effectively with abuse it is essential for them to work through their own attitudes and feelings.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 134
Abuse is a term which covers a wide range of circumstances. involved in our mission,. (As YWAM, we apply this to vulnerable adults as. (As YWAM, we apply this to vulnerable adults as well) Also for adults the UN Universal Declaration of Human Rights with particular reference to Article 5 which states: No one shall be subjected to torture or to cruel, inhuman or degrading treatment or punishment. Abuse tends to be divided into several main headings: physical abuse, neglect, emotional abuse, sexual abuse, financial abuse and spiritual abuse. Within each type there is a continuum of severity. Whatever form the abuse takes and whoever the abuser, the parents or caretakers nearly always have some control or degree of responsibility for what happens. Parents or caretakers can harm young people either by direct acts or by a failure to provide proper care, or by both. 2.1 Definitions of types of abuse Abuse Covers: Physical Injury Any physical injury to a child or young person or vulnerable adult caused by a family member or other person with responsibility for their care. Neglect A failure to meet a child’s, young person’s or vulnerable adult’s needs for food, warmth, protection and care. Emotional Abuse The persistent, severe emotional ill treatment or rejection that severely effects the emotional and behavioural development of the child, young person or vulnerable adult. Sexual Abuse Involving a child, young person or vulnerable adult in sexual behaviour or activities to meet an adult or child/young person’s needs. It can involve direct physical contact or activities where no physical contact is made, such as making a child or young person watch a sexual act. Financial Abuse A carer or family member depriving a child, young person or vulnerable adult of money or possessions that are rightfully his or her own. Spiritual Abuse The misuse or abuse of spiritual authority to control or coerce children and vulnerable adults into behaviours that met the abusers own needs; the misuse of spiritual authority to control or coerce others into any other forms of abuse, physical, sexual, financial, etc. Domestic Violence While not a form of abuse on its own, usually involves more than one area of abuse, e.g. physical, psychological, or sexual violence, that takes place within an intimate or family-‐type relationship and forms a pattern of coercive and controlling behaviour. Includes the suffering experienced by children when witnessing the ill-‐ treatment of another person. 2.2 Physical signs • Any injuries not consistent with the explanation given for them. • Injuries which occur to the body in places which are not normally exposed to falls, rough games, etc. • Injuries which have not received medical attention. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 135
• Neglect -‐ undernourishment, failure to grow, constant hunger, stealing or gorging food, untreated illnesses, poor hygiene, inadequate care etc. • Repeated urinary infections or unexplained tummy pains. • Instances where children are kept away from the group inappropriately. • Reluctance to change for, or participate in, games or swimming. • Bruises, bites, burns, fractures, etc. which do not have an accidental explanation. • Cutting/scratches/drug abuse or other forms of self-‐harm. 2.3 Emotional signs • Changes or regression in mood and behaviour, particularly where a child withdraws or becomes clinging. Also depression/aggression, extreme anxiety. • Nervousness/frozen watchfulness. • Obsessions or phobias. • Sudden under-‐achievement or lack of concentration. • Inappropriate relationships with peers and/or adults. • Attention seeking behaviour. • Persistent tiredness. • Running away/stealing/lying.
2.4 Indicators of possible sexual abuse • • • • • • •
Any allegations made by a child concerning sexual abuse. Child with excessive preoccupation with sexual matters and detailed knowledge of adult sexual behaviour, or who regularly engages in age-‐inappropriate sexual play. Sexual activity through words, play or drawing. Child who behaves in a sexually provocative or seductive manner with adults or other children/young people. Inappropriate bed-‐sharing arrangements at home. Severe sleep disturbances with fears, phobias, vivid dreams or nightmares, sometimes with overt or veiled sexual connotations. Self harm or Eating disorders -‐ anorexia, bulimia.
2.4-‐rearing do not justify child abuse. It is important that the above signs are not taken as indicating that abuse has taken place, but the possibility should be considered. It is important to recognise that people who abuse children come from all backgrounds, including Christians, married and single, men and women of all ages and young people themselves. The Home Office have published guidance in the form of a booklet on Caring for young people and the vulnerable - guidance for preventing abuse of trust. At YWAM we undertake to follow the principles found within the Abuse of Trust guidance issued at the Home Office. It will therefore be unacceptable for those people in a position of trust to engage in any behaviour which might allow a sexual relationship to develop whilst in a relationship of trust.
3. WHAT TO DO IF YOU HAVE CONCERNS OR SUSPICIONS ABOUT ABUSE OF ANY KIND Your first priority must be the interests of the young or vulnerable person and any others who may also be at risk. The protection of young and vulnerable people must take precedence over any desire you may have to raise concern with the person who might be responsible. Remember that abuse is a crime. It is in the best interests of both parties to YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 136
involve the statutory authorities from the very beginning. YWAM has no need to fear statutory authorities -‐ they have been established by God (Romans 13 v 1), and need all our support in their very difficult work.
3.1 Suspicions or concerns about abuse Chain of Communication:
There is a chain of communication for any suspicion or allegation of abuse. You must report concerns as soon as possible to the lowest person on the chain that is available. • Your Base or Team Leader. If there is no Base/Team leader appointed, the matter should be brought to your ministry leader. If suspicions/allegations involve this leader, contact ST directly. • Safeguarding Team (ST): See names and contact details on page 2. If suspicion/ allegation involves someone on the ST, contact another person on ST or contact CCPAS directly. • Churches Child Protection Advisory Service (hereafter CCPAS), PO Box 133, Swanley, Kent, BR8 7UQ. Telephone 0845 120 45 50. If a report is made to the CCPAS first you should contact the nominated ST within one working day. • Local Children’s or Adult Services, as appropriate. • Any ministry or base leader being made aware of a concern, whether minor or not, MUST at as soon as possible contact one of the ST people named above, and confirm in writing what has been said. Base, team and ministry leaders have NO discretion over whether or not to refer the matter. (This means that the leader HAS NO CHOICE, the incident MUST BE REPORTED!) • The Safeguarding Team (ST) will meet and give further advice and oversight in response to any issues raised. • You should not discuss your suspicions with anyone other than those people given above, and do not discuss with parents/carers! • You must make written, dated notes of everything that occurred, what you saw/heard, etc., preferably within an hour of the suspicion/allegation. Keep these notes in a safe place, and do not discard even if typed up/photocopied later. See Safeguarding Referral Form. • It is of course the right of any individual as a citizen to make direct referrals to the child protection agencies or seek advice from CCPAS. However, we hope that members of YWAM will use this procedure. If however, you feel that none of the above has responded appropriately to your concerns, then it is open to you to contact the relevant organisation directly. We hope that by making this statement we demonstrate the commitment of YWAM to effectively protect children and vulnerable adults. • YWAM will support the ST in their role, and accept that any information they may have in their possession will be shared in a strictly limited way on a need to know basis.
3.2 Allegations/Suspicions of physical injury or neglect Lesser Concerns:
•
•
Where poor parenting, neglect, etc. is suspected, encourage parent/carer to contact their Health Visitor/Doctor/Social Worker. Keep written, dated notes of all that was seen/ suspected/ communicated and the response and inform your Base/Team/Ministry leader as soon as possible. Leader must inform ST within 24 hours. If a parent/carer is unwilling to accept help or fails to acknowledge need for medical attention, keep written, dated notes of all that was seen/ suspected/
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 137
communicated and the response, and use the following chain of communication starting at the lowest level available within 24 hours: Base/Team/Ministry Leader >> ST >> CCPAS >> Local Children’s/Adult Services Serious Concerns:
•
Where there are serious concerns regarding the child/vulnerable adult or their parents/carers (in cases of deliberate harm or where the is a risk of significant harm) or where a child or vulnerable adult is afraid to return home, use the following chain of communication starting at the lowest level:
Base/Team/Ministry Leader >> ST >> CCPAS >> Local Children’s/Adult Services
3.3 Allegations of sexual abuse Every suspicion/allegation of sexual abuse is to be seen as serious. The same chain of communication must be followed IMMEDIATELY. • Contact your Base/Team/Ministry Leader IMMEDIATELY. • The Base/Team/ Ministry leader will contact the ST IMMEDIATELY. • The ST will contact the Social Services Child Protection Officer, Police Child Protection Team directly. The Base/Team/ Ministry leader and the ST will NOT speak to the parent (or anyone else). • You should not discuss your suspicions with anyone other than those nominated above. • Neither you nor your Base/Team/Ministry Leader should investigate the concern – this is for Social Services and/or Police to do. Your role is to report, keep the child/vulnerable adult safe, and keep accurate records. • If for any reason the ST is unsure whether or not to follow the above then advice will be sought and followed from CCPAS. The agency will confirm its advice in writing in case this is needed for reference purposes in the future. • Under no circumstances will the ST attempt to carry out any investigation into the allegations or suspicions of sexual abuse. The role of the ST is to collect and clarify the precise details of the allegation or suspicion and to provide this information to the Social Services Department, whose task is to investigate the matter under Section 47 of the Children Act 1989. • Whilst allegations or suspicions of sexual abuse will normally be reported to the ST, the absence of the ST should not delay referral to the Social Services Department. • Exceptionally, should there be any disagreement between the person in receipt of the allegation or suspicion and the ST as to the appropriateness of a referral to the Social Services Department, that person retains a responsibility as a member of the public to report serious matters to the Social Services Department, and should do so without hesitation. • YWAM will support the ST in their role, and accept that any information that may from time to time be in their possession will be shared in a strictly limited way on a need to know basis. • Not withstanding these procedures, individuals with responsibility should take appropriate action within the principles of the procedure, if they are unable to contact the appropriate leaders.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 138
4. HOW TO REACT WHEN A YOUNG PERSON OR VULNERABLE ADULT WANTS TO TALK ABOUT ABUSE (DISCLOSURE) 4.1 General Points: CHILD • • • • • • • • • •
Above everything else listen, listen, listen! Accept what the child says (however unlikely the story may sound). Keep calm. Look at the child directly. Be honest. Let them know you will need to tell someone else – – recording accurately the words used by the young person.
4.2 Helpful things to say or show • • • • • • •
I believe you (or showing acceptance of what the child says). Reflective statements, to clarify you have understood what is being said. You've done the right thing in telling me. That must have been really hard/sad/difficult. (use age appropriate language without leading or inciting). I am glad you have told me. It's not your fault. I will help you.
4.4 Concluding • •
Again, reassure the child that they were right to tell you and that you believe them. Let the child know what you are going to do next and that you will let them know what happens (you might have to consider referring them to Children’s Social Services or the Police to prevent a child or young person returning home if you consider them to be seriously at risk of further abuse).
4.5 General Points: VULNERABLE ADULT • • • • • • • •
Above everything else listen, listen, listen! Accept what the person says (however unlikely the story may sound). Keep calm. Look at the person directly. Be honest. Let them know you will need to tell someone else – don’t promise confidentiality. Even when someone has broken a rule they are not to blame for the abuse. Be aware that they may have been threatened or bribed not to tell.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 139
• • •
Never push for information. If the person decides not to tell you after all, then accept that and let them know that you are always ready to listen. As soon as possible write down what has been shared – recording accurately the words used by the young person. Even if you do not have their permission, but you are concerned for their safety or that of someone else, you still report it! (Consent can be legally waived in this instance.)
4.6 Helpful things to say or show • • • • • • •
I believe you (or showing acceptance of what the person says). Reflective statements, to clarify you have understood what is being said. You've done the right thing in telling me. That must have been really hard. I am glad you have told me. It's not your fault. I will help you.
4.8 Concluding • •
Again, reassure the person that they were right to tell you and that you believe them. Let the them know what you are going to do next and that you will let them know what happens (you might have to consider referring them to Adult Social Services or the Police to prevent a person returning home if you consider them to be seriously at risk of further abuse).
5. WHAT TO DO ONCE A CHILD/VULNERABLE ADULT HAS TALKED TO YOU ABOUT ABUSE •
•
Make notes as soon as possible (preferably within an hour of the interview), writing down exactly what the person said, and when she/he said it, and what was a happening immediately beforehand (e.g. description of activity). In cases of physical abuse, record any injuries noticed on the child and their location e.g. cut on third finger of right hand. Record dates and times of these events and when you made the record. Keep all handwritten notes, even if these have subsequently been typed up for an indefinite period in a secure place. (A record sheet is an appendix to this policy, which is there to help, but not replace, personal notes.) Report the allegation, using the following chain of communication starting at the lowest level: Base/Team/Ministry Leader >> ST >> CCPAS >> Local Children’s/Adult Services
•
You should not discuss your suspicions or allegations with anyone other than those nominated above. Deception and denial are often present where there is child abuse which is why it is crucial that the policy is followed and that you do not confront/question the person suspected of the abuse however unbelievable the allegations seem to you.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 140
•
Monitor and be aware of your own feelings, seek pastoral support if needed, while maintaining confidentiality.
Reasons for Not Contacting the Parent/Carer or Alleged Abuser • •
•
A child, young person or vulnerable adult might make a direct allegation of abuse naming the person who did it. Because of fear, confusion or other reasons the allegation might not be wholly accurate. Informing a parent/carer of the allegation could damage any subsequent investigation by the statutory authorities if their reaction inadvertently alerts the person under suspicion e.g. the parent/carer going to see them to sort the matter out. It is vital no one from the organisation informs the parent/carer of the allegations at this stage. This decision should be left to the statutory authorities. Another very important reason the alleged abuser is not contacted is that they could try to silence their victim with bribery or threats. Also, they could dispose of any incriminating material such as books, videos, DVDs, photos, computer files or text messages.
6. SAFE APPOINTMENT OF YWAM WORKERS/TRAINEES Selecting and appointing workers: • • • •
The principles governing these appointment procedures apply to applicants for YWAM staff positions, volunteers, mission builders, and trainees on ALL YWAM residential courses. Under NO circumstances should shortcuts be taken e.g. references overlooked, incomplete applications accepted etc. The application screening process for all positions should include more than one person. Current operating procedures may not yet take into account all that we are recommending, and these must now be reviewed and brought into line with this Policy.
Experience has shown that the most frequent method of infiltration of an organisation by paedophiles has been through an existing member of the organisation exerting undue authority to have the normal processes shortened. From April 2002, new procedures were introduced enabling churches and other organisations to obtain criminal record checks on any staff member or trainee working with children or vulnerable adults via the Disclosure and Barring Service (formerly Criminal Records Bureau). YWAM may, with permission, use a previously issued DBS Enhanced Disclosure dated after 17 June 2013, ONLY IF it is for both CHILD AND ADULT WORKFORCE and applicant has joined the DBS Update Service. YWAM England good practice is that all staff regularly read and sign an internal safeguarding document. In new legislation passed in 2012, the Criminal Records Bureau and Independent Safeguarding Authority have been combined into a new organisation, the Disclosure and Barring Service (DBS). All
references to the CRB/ISA in this or other YWAM England documents will apply to this new organisation and its procedures. The legal position is that children and youth work is exempt from the Rehabilitation of Offenders Act 1974, and all convictions, however old, which relate to children and young people, must be declared by applicants, if asked. However, someone wanting to conceal their past may not of course, tell you. The selection process MUST include the following:
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 141
• • • •
The applicant must complete the appropriate application form giving information as to their name (and previous names), date and place of birth, and current and 5 year address history. The Application must contain questions about experience and attitudes to young people. The application must either have the Self-Disclosure Form attached, or it must contain the following questions: Have you ever been charged with, cautioned or convicted in relation to any criminal offence not subject to DBS filtering rules (as found at and ); or are you at present the
• •
•
•
• • • •
subject of a criminal investigations/pending prosecution? o This should include relevant police non-‐conviction information not subject to DBS filtering rules(as above). Have you ever been the subject of a police investigation that didn’t lead to a criminal conviction? To your knowledge have you ever had any allegation made against you, which has been reported to, and investigated by, Social Services/Social Work Department (Children’s or Adult Social Care)? Has there ever been any cause for concern regarding your conduct with children, young people, or vulnerable adults? Please include any disciplinary action taken by an employer in relation to your behaviour with adults. o Have you ever had an offer of work with children/young or vulnerable people declined? o (These questions are appropriate even if the applicant is not applying to work with children and/or vulnerable adults because of the close quarters in which most staff and trainees and their families live) References from those who know the person well e.g. previous church leaders, employers, friends asking explicitly about their suitability to work with children/vulnerable adults. Applicants for training and/or staff positions involving work with children and/or vulnerable adults must complete and sign a Self Disclosure Form, giving permission to run or update a police check (see appendix: Self Declaration Form). (For current advice on who needs a DBS check, contact local DBS “recruiter” for your location or the Safeguarding Team) If the applicant has not been in the UK for over a year, then the applicant must supply a current police check from their country of residence, if possible. The Self-Disclosure Form must still be completed by the applicant, whether or not they are able to provide a police check. Ideally, checks should cover 5 years of address history. Good practice may include foreign police checks for overseas staff who have been in the UK for less than 2 years. If it is not possible to get the police check in English, Personnel/Registrar staff may at their discretion use a trusted YWAM staff member who is fluent in the language of the police check and English to do a translation, upon completion of the YWAM England Translation Contract, in appendix. Any issues arising from DBS Disclosures are to be referred to the Safeguarding Team for consideration before the person is accepted/rejected. Wherever possible an interview before appointing, or if not, on arrival. Interviews must take place with all workers before the 3 month review confirming appointment, with the exception of trainees and short term placements [3 months or less]. As soon as possible after arrival, and before the 3 month review meeting, all workers should have YWAM’s Safeguarding Policy explained, and expectations of them in relation to good practice. (Trainees should do this during the briefing week at the start of each school.)
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 142
• •
•
The confirmation of appointment process should include views from immediate superior and other members of the community. If a staff member who is well known to us applies to change roles to one requiring a DBS check, but they do not have the required ID documents (e.g. trouble obtaining bank account), it may be decided by leadership ON A CASE BY CASE BASIS to allow them to participate SUPERVISED while they are obtaining the necessary documents. If non-‐UK applicant is unable to obtain a police check from their home nation, SUPERVISED work with children and/or vulnerable adults may be allowed if the applicant is well known to us, at the discretion of the leadership upon completion of the Self-Disclosure Form and appropriate Safeguarding training.
As YWAM staff often change roles, and as we encourage all staff to be involved in outreach at various times, we must be vigilant to ensure that the Self-Declaration Form and police check is completed/updated by each staff person engaging in work with children/vulnerable adults.
6.1 Criteria for NOT appointing workers • • •
Under no circumstances should a person with a known previous history of abusing, or persistent temptation in this area, be appointed to ANY YWAM position, including trainee or volunteer. Under no circumstances should a person be allowed to work with children and/or vulnerable adults if they refuse to submit their DBS Disclosure Certificate (and update service permission, if appropriate) for appraisal. Abusive practices against young people are addictive, and even when there is repentance it would be wrong to place an individual in a position of temptation and this policy is as much for the benefit of the adult concerned as for the young or vulnerable people.
6.2 Accepting Young People as Volunteers/Trainees/Long Term Guests Under British law, we carry greater responsibility for caring for a volunteer, trainee or guest who has not yet reached their 18th birthday. Whilst it is usual practice to only accept adults as volunteers, trainees or unaccompanied guests, we recognise that on occasion you may wish to issue an invitation to a young person. The following guidelines are in place for such a situation: All situations involving young people coming as unaccompanied volunteers or long term guests must be approved by the Safeguarding Team. Trainees may be accepted for DTS at 1. the discretion of the school leader if they will turn 18 during the course of their school; trainees younger that this may be accepted in exceptional situations with the approval of the Safeguarding Team. 2. Before the young person is accepted, the In Loco Parentis form must be signed and returned by the parents/carers and a trusted staff member acting In Loco Parentis while the young person is with YWAM England. 3. The staff member agreeing act “In Loco Parentis” for the young person, will a. Live on location with the young person (not necessarily in same dorm/flat, depending on age appropriateness) b. Have a current DBS Enhanced Disclosure covering Child Workforce; c. Assume responsibility for the young person’s safety and well-‐being; d. Establishing good two-‐way contact with the young person’s parents/carers and with the young person themself; e. Agree with the parents/carers on aspects of care such as education, work, boundaries, etc. 4. Before the young person is accepted, a risk assessment must be done in terms of Safeguarding and Health and Safety. 5. Upon arrival of the young person, the In Loco Parentis staff member should YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 143
a. Help the young person adjust to his/her new surroundings, introduce them to other YWAMers, etc.; b. Establish a good relationship with them; c. Continue good communication with parents/carers; d. Liaise with the young person’s work/course leader regarding expectations, work load, hours, etc. (e.g. a younger person may require more breaks, shorter hours, more help) 6. A one-‐month trial is highly recommended, after which the young person, In Loco Parentis staff member, and parents/carers opinions are sought on whether the situation is working well.
6.3 Legal Age Regulations for UK If the young person is not from the UK, guidance will need to be communicated with the parents/carers regarding certain legal age limits in the UK. If these limits differ from their home situation, guidance may be needed (in communication with parents/carers) to help the young person make wise decisions. According to new legislation, beginning in September 2013, a young person must be in full or part time education until the age of 17; in September 2013 this age will rise to 18. At the Age of 16, a young person can legally
• • • • • • • •
Buy and drink beer or alcoholic cider to have with a meal in a pub, restaurant or hotel; Buy liqueur chocolates; Register as a blood donor (but not able to donate until age 17); Buy cigarettes and tobacco; Leave home without consent of parents/carers; Choose their own doctor and consent to medical or dental treatment; Apply for a passport with consent of parents/carers; Consent to sexual intercourse with another person over the age of 16;
At the age of 17 a young person can legally:
• • •
Have a licence to drive a car, small goods, vehicle or tractor on a public road (but not drive a YWAM vehicle; most vehicle rental agencies require a person to be over 25); Donate blood without consent of parents/carers; Be interviewed by the police without an appropriate adult present.
At the age of 18
At the age of 18 the person legally becomes an adult and all legal activities are permissible.
7. CREATING A SAFE ENVIRONMENT 7.1 Background YWAM gives Christians the opportunity to demonstrate the love of God to all people. We are God’s agents, and carry a major responsibility in interpreting the character of God as accurately as we can. Because young people and those in need are so precious to God, and because we represent God, it is of paramount importance that absolutely nothing happens which betrays or seems to betray the trust which young people and their families place in us, or leaves us open to suspicion or accusation. Attempts to establish inappropriate, intimate emotional or physical relationships with young or vulnerable people will be destructive to that person and the workers concerned and betray the trust of the person’s family. A fundamental part of encouraging a young person in their relationship with God is the building of trust. Adults involved in Christian care, teaching and activities with young or YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 144
vulnerable people have a very important responsibility both on a practical and spiritual level. A balance needs to be achieved between positive attempts to encourage the young person spiritually, look after them physically and provide an appropriate standard of structure and discipline. Most young people enjoy physical contact with adults: some do not. It is the young person who needs to make the choice whether they have physical contact or not; e.g. if a child is upset, the adult should ask the child if they mind them putting an arm around them. It is extremely important for both the well-‐being of the young person, and your own protection, that physical contact only takes place which is appropriate for the situation and age of the young person. Even if praying for or with someone, only touch with permission and only in appropriate circumstances where others can see you.
8. SUPERVISION AND GOOD PRACTICE REGARDING CHILDREN/YOUNG PEOPLE AND VULNERABLE ADULTS (For Vulnerable adults, the principles below apply, but please use your judgement, depending on the ability of the person involved, e.g. if a person’s ability is below an average 8 year old, you may need to use the group ratio mentioned, etc., depending on the situation. Remember that records are always a good idea! If in doubt about good practice with vulnerable adults, please consult your team/ministry/base leader, ST, or CCPAS) • All activities should have at least two adults present, preferably three. The ratio of young people to adults may vary according to age and activity, but should not be less than 1 adult per 8 children under 8. • For children over 8 years of age there is no official ratio. A suggested ratio is 2 adults (preferably one of each gender) for up to 20 children, with an additional leader for every 10 children. • If young people of both sexes are present, even if only one, then there must be a worker of each sex present. • A worker should not be alone with a young person where their activity cannot be seen. This may mean leaving doors open, or two groups working in one room. In a situation where privacy and confidentiality are important, another adult should know that the meeting is taking place, and the open door policy should be maintained. There should be another adult close by in the building and the young person must know that they are there. • Have a clear strategy for summoning additional help (if needed) in situations where a worker is alone with a child (e.g. small Sunday school classes) • The level of personal care (e.g. toileting) must be appropriate and related to the age of the child whilst also accepting that some children have special needs. You need a parent’s written permission before undertaking intimate personal care. • No person under 16 years of age should be left in charge of any children of any age. Nor should children or young people attending a group be left alone at any time. • Ensure that the only people allowed to participate in a children's activity are the workers assigned to that group. Other adults should not be allowed free access. • All youth activities (under 18 years of age) should be overseen by named adults who have been cleared by the relevant authorities (DBS (FORMERLY CRB) etc.) • Ensure that others know of all your activities as a worker, that everything is open and up front, with nothing being covert.
8.1 Boundaries Treat all young people and vulnerable adults with respect and dignity; watch your language, tone of voice and body language. Listen well, and value their words. Do not engage in any of the following: • Invading the privacy of young people/vulnerable adults when changing, showering or toileting, except when there are special needs or circumstances (and then only with prior permission).
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 145
• • • •
Rough, physical or sexually provocative games. Making sexually suggestive or flirtatious comments to or about a young person/vulnerable adult. Inappropriate or intrusive touching in any way. Any ridiculing, bullying, scapegoating of a young person/vulnerable adult.
Workers should be able to control and discipline young people without physical means. If you invite a young or vulnerable person to your home, ensure this is with the knowledge of your co-‐workers, and that a parent or guardian is aware. You must not invite a young or vulnerable person to your home alone. If you are showing a film/playing a computer game ensure that the age classification is followed and even then caution needs to be exercised with regard to suitability of content.
8.2 Keeping Records • • •
A register of children/young people/vulnerable adults and helpers at an activity should be kept. This should include a record of arrival and departure times. A note should also be made of other people in the building (e.g. maintenance people, visiting speaker etc.) A logbook should be considered for noting down unusual events or converSTions that are witnessed. A record of similar events/occurrences may help highlight patterns that might otherwise not be so obvious.
8.3 Talking and Listening to Children/Vulnerable Adults Whilst many churches have appointed adults to listen to and talk with children or vulnerable adults, it must be remembered that they will often decide for themselves who they want to talk to. They might test him/her out in some way before they are prepared to talk. Because of this, all adults, whether or not they work with children/vulnerable adults, need to understand the importance of listening and responding appropriately. When promoting the "listener's" role, children and young or vulnerable people will not always understand jargon, such as "advocate" or "independent listener". What is important is to identify ways to communicate effectively to all people that they are valued, that what they say is important and that there are people who are happy to listen to them. If a child or vulnerable adult wants to talk: • Suggest where you might meet. • Offer a child/young person or vulnerable adult privacy but remember their and your safety: e.g. make sure there is another adult nearby and the child knows this, keep the door ajar, etc. • Remember not to promise confidentiality. • A child/young person or vulnerable adult may not want to talk about abuse. • Be aware of how to respond if a child/young person or vulnerable adult does disclose abuse. (See section 3.2)
8.4 Working with disruptive children If a child/young person or vulnerable adult is being disruptive they may endanger themselves/ or others: • Ask them to stop. • Speak to the child or vulnerable adult to establish the cause(s) of their upset. • Inform them that they will be asked to leave if their behaviour continues. • Warn the child or vulnerable adult that if they continue to be disruptive, this might result in longer-‐term exclusion from the group or activity. If a child/young person or vulnerable adult is harming themselves, another person or property, then other young or vulnerable people should be escorted away from the area. At the same time, and with a second worker present, request the child/young or vulnerable person to STOP. If this request is ignored then inform the person that you will consider calling additional help (e.g. Police) if they do not stop. Only in extreme circumstances, you may need to restrain the child/ young person to prevent them harming themselves/ others/ property, whilst you wait for the police. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 146
The workers involved should always record what happened as soon as possible after the incident. This should include the following: • What activity was taking place. • What might have caused the disruptive behaviour. • An account of the child's/ young person's or vulnerable adult’s behaviour. • What you said and how you and others responded. • A list of others present who witnessed the incident.
8.5 Giving Lifts to Children or Vulnerable Adults •
• • • •
•
• •
Do not give lifts to young people or vulnerable adults on their own other than for short journeys. If they have to be alone ask them to sit in the back of the car. You may also wish to look at whether a worker should transport children if they have motoring offences. The distance of travel (short or long) may not have a bearing on the safety of the child being transported on their own. The obvious exceptions should be when a worker is aware that a child or vulnerable adult has a crush on them, in such circumstances it would be wise for another worker to provide transport, or take several children and drop off this child first or in the case of a vulnerable adult take a second person or chaperone. Only those who have gone through YWAM's recruitment procedures should transport children. All drivers should have read the Child Protection policy and agreed to abide by it. Parental consent should be given and all journeys should be carried out with the knowledge of the leader of the activity concerned. Drivers should not spend unnecessary time alone in a car with a child or vulnerable adult. If a child wants to talk to a driver about something and has waited until other children are dropped off, the driver should explain that it isn't convenient to talk there and then, but arrange to meet the child/young or vulnerable person at a location where there are other adults around. When travelling in groups with more than one vehicle it is good practice to insist children stay in the same groups on the out-‐going and return journey. This will avoid the confusion over whether a child has been transported home or, at worst, left behind. Similarly for vulnerable adults; know who you are responsible for and make sure you have all your passengers. Please note the maximum speed for a minibus is 50mph on single-‐carriageway roads, 60mph on dual-‐carriageways, and 70mph on motorways. At collection or dropping off points do not leave a child on their own. Make sure children are collected by an appropriate adult – known to the child and agreed in advance. Some vulnerable adults maybe able to look after themselves if in doubt ask.
8.6 Residential Activities Consider carefully arrangements for residential activities. We advise that it would be unwise for a worker to share accommodation with one or two children, though a larger dormitory may be acceptable. The exception to this is where the worker is the parent of those children. CCPAS suggest that organisations use log books for the various children’s activities as a way of safeguarding both children and workers. Workers are safeguarded from any false allegations as a log book would demonstrate: names of children or vulnerable adults present, names of all adults present and any significant incident -‐ a fight broken up by adults, children asked to leave, or vulnerable adult having a tantrum etc. -‐ any allegations made. All workers who witnessed, heard or responded in any way should record details, sign and date log book. The appropriate written permissions must be obtained from parents/carers for all residential activities of those under 18 , and parents/carers must be given contact details of person in charge of their child for the duration of the activity. For activities of a longer duration, such as the Discipleship Training Schools, with trainees under the age of 17, the “In Loco Parentis” form should be used (see appendix) with a person on the base/team designated as the main carer for this time. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 147
8.7 Helping children or vulnerable adults protect themselves It is important to teach children and vulnerable adults personal safety. The gospels in particular are an excellent resource. Through presenting the story of, for example, the prodigal son and the restored relationship with his father, children and vulnerable adults can be helped to understand physical contact that is good and healthy, acknowledging there are other touches that are unwelcome or wrong. It may also help to discuss concerns or talk about situations where the child or vulnerable adult feels uncomfortable or unsafe. Touch or physical contact between adults and children, can be healthy and acceptable in public places, but discouraged in circumstances where an adult and child are on their own (except, of course, within family relationships but even there it can go horribly wrong.) Web-‐sites with good advice and information regarding keeping children safe are: CCPAS: CEOP: Kidscape: NSPCC:
8.8 Safety Before undertaking any programmes check for any legal requirements. Under no circumstances should YWAM workers engage in any activity for which they are not qualified or which places young people at inappropriate risk. Workers involved in activities for young or vulnerable people should check that any building or equipment used is safe, conforms to any regulations. They should be aware of fire procedures, and ensure that they are known and observed.
8.9 Feedback If you see a fellow worker acting in ways which give rise to concern, or which might be misconstrued, be prepared to speak to them or a senior colleague about your concerns, within the guidelines of this policy. The safety of the young or vulnerable person must come first, even before loyalty to your colleagues. There should be an atmosphere of mutual support, trust and care which allows all workers to be able to discuss inappropriate attitudes and behaviour.
8.10 Staff Meetings • • •
Regular meetings should occur to review procedures and discuss concerns, and clarify any questions. Staff should report back to such a meeting if departure from the guidelines becomes necessary, which provides protection to the individual and draws the leadership’s attention to problem areas. Keep a written record of issues and decisions discussed at such meetings.
9. THE INTERNET Development of the internet has revolutionised communication systems throughout the world and if used in the right way is an excellent resource. However, care in its application needs to be exercised so that the safety of children and vulnerable adults is not compromised. Children and vulnerable adults need to be aware of on-‐line safety in the same way they are taught road safety. We are currently in an age of technology where young people are more vulnerable than ever. Connecting & belonging are very important to a young person and online communities provide a quick and easy fix for this. Though much of what happens online is harmless there are plenty of risks that most young people are completely unaware of, from simple misunderstandings to the more serious online predators. Each time a person logs on they put themselves in a very vulnerable position. Youth With A Mission wants to be seen & known as a safe place with trustworthy staff. We also want to be above reproach and transparent in all our online actions. The following practices will be helpful in guiding you to have safe online relationships online with children and vulnerable adults who you may come in contact with as a result of your YWAM activities.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 148
9.1 Website Do's and don'ts • • • • •
•
When designing a web-‐site, make clear what is available for copying and what is not and don't refer to other sites without permission. Personal e-‐mail or postal addresses, telephone or fax numbers must not be divulged. Get your web-‐site rated through the "Recreational Software Advisory Council's RSACi system. or Safesurf rating Standard at. To make web content accessible to people with disabilities look at for the Web Content Accessibility Guidelines. If web access is being provided for children or young people then consider using filtering software to prevent access to inappropriate web sites e.g. Netnanny, Cyberpatrol or Surfwatch etc. Your internet service provider may also have filtering software. If you are providing web access e.g. cyber café, ensure that all users complete an internet permission form including parental permission.
9.2 Social Networking: Adding Minors as a Friend or Follower DO : •
Start a ministry account on your social network of preference, and accept friend requests from children and/or vulnerable adults to be added to this rather than to your own personal account, unless you know them personally outside the ministry situation (eg. Family friend).
DO NOT : • Add or pursue relationships with people under the age of 18 on your personal online social network account – let it be initiated by the minor. Accepting a request is up to your own discretion and at your own risk. • Add/friend anyone under the minimum age allowed on the online service. For example Facebook prohibits those under the age of 13 so no staff member should contact any minor on Facebook under that age.
9.3
Social Networking: Posting Content Online
DO : •
Make sure your online content remains appropriate for children under the age of 18 at all times. Your online profile should model our values and codes of conduct. Consider asking a spiritual advisor or leader to look at your online profile and give you feedback on what it reflects about your values.
DO NOT : • Post photos or videos with children or vulnerable adults in them unless you have permission. Ministries will often have written permission and the legal right to upload and use images and videos of their activities on their sites – check with your leaders if you are doing this. However, as a member of YWAM you do not have the legal right to post any images or videos on your personal web page without written consent from the minor and parent. This includes Facebook, blogs and newsletters. • Post photos of individual children; instead use a group photograph. However, DO NOT USE any photo if a child can be identified by their name or the location they are in and never provide names, addresses or locations. This could inadvertently help a sex offender to identify or gain access to a child or vulnerable adult. • Tag photos with names of minors, or allow someone else to tag your photos with the minor’s name, without written parental permission.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 149
9.4 Communicating With Minors Online DO : •
Treat webcams/skype/etc. communication the same as being with them in person, i.e. do not do, talk about, or show anything that you would not do if you were there with the person, including not being alone! DO NOT : • Initiate a chat or online conversation. • Engage in private communication with a minor (without prior permission from parent). Private communication is defined as any communication that cannot be actively monitored by someone else. (ie. MSN Messenger, Facebook Chat/Messages, AIM) • Communicate online your thoughts and views about any inappropriate online behaviour from a minor.
9.5 Reporting an Online Incident What is worth reporting? An incident is any unplanned occurrence that could possibly be considered negative by a parent, a minor, social services, or the YWAM ministry concerned. If you are in doubt as to whether an incident is grave enough to report, report it to your team leader. 1. If you view or are involved in an incident online do not respond in any way online. 2. If possible copy the conversation or post. 3. Report & Record (including the copied post) the incident to your team leaders as soon as possible 4. Team Leaders can help you decide if further action is required, e.g. informing parents, reporting the situation to the Safeguarding Team. For further information see:, or.
10. DATA PROTECTION PRINCIPLES, FILMING AND PHOTOS The Data Protection Act 1998 is designed to provide privacy protection for individuals about whom personal identifying data is kept. It lays down 'best practice' principles for those who keep data and it applies to paper records as well as computerised information. The Act covers the whole of the UK, and all organisations must comply with the rules on processing data. "Processing" includes obtaining, recording, holding or storing information and carrying out any action on the data, including adaptation, alteration, use, disclosure, transfer, erasure and destruction. • Personal data shall be processed fairly and lawfully. • Personal data shall be held only for one or more specified and lawful purposes and shall not be further processed in any manner incompatible with that purpose or purposes. • Personal data shall be adequate, relevant and not excessive in relation to the purpose for which it is processed. • Personal data shall be accurate and, where necessary, kept up to date. • Personal data processed for any purpose shall not be kept for longer than is necessary for that purpose. According to our insurers, regarding staff/trainee files this is 50 years! • Appropriate technical and organisational measures shall be taken against unauthorised or unlawful processing of personal data and against accidental loss or destruction of the data. • Personal data shall not be transferred to a country or territory outside the European Economic Area unless that country or territory ensures an adequate level of protection for the rights and freedoms of data subjects in relation to the processing of personal data.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 150
10.1 Taking Photos/ Video footage of children • • • •
• • •
Permission (verbal or written) must be obtained of all the people (children and adults) who will appear in a photograph, video or web cam image before the photograph is taken or footage recorded. It must be made clear why that person's image is being used, what you will be using it for, and who might want to look at the pictures. If images are being taken at an event attended by large crowds, such as a sports event, this is regarded as a public area and permission from a crowd is not necessary. If photographs or recordings of children's/ youth groups or vulnerable adults are made and individual children or vulnerable people can be easily identified, children's / youth leaders / staff workers must find out whether any parents/guardians do not want those they care for to be photographed or recorded. Children and young people under the age of 18 should not be identified by surname or other personal details. These details include e-‐mail or postal addresses, telephone or fax numbers. When using photographs of children and young or vulnerable people, it is preferable to use group pictures. Obtain written and specific consent from parents or carers before using photographs on a website.
11. PASTORAL AND SPIRITUAL CARE •
•
•
• •
•
Counselling should only be undertaken by people who have been trained and accredited by an approved body and who are being supervised. Of course there are situations where young people or vulnerable adults might talk informally or need practical advice. This is not counselling, and you should realise/know your limits. Prayer and ministry with young people/vulnerable adults should always take place within the principles or guidelines of this policy e.g. pray for same-‐sex or have another person present preferably of the same-‐sex as the child/adult. Do not lay hands on the person without their permission and place hands in appropriate place e.g. shoulder/arm. Ministry should be age appropriate, non-‐threatening, and sensitive to young people’s/vulnerable adults’ and parent’s or carers’ church background. Deliverance ministry should never take place outside of the context of the churches own pastoral and family situation and never without the understanding and agreement of the person receiving prayer. Great pastoral care is required over the exercise of spiritual gifts e.g. words of knowledge. Those exercising spiritual gifts should always remember the effect such information is likely to have on the person receiving it. The Bible also tells us to test these gifts (1 John 4:1) and so any such word of knowledge should not be treated lightly but investigated thoroughly. Create an environment where young people and vulnerable adults feel safe and that they will be listened to and valued. Encourage them to think through their own emotions, responsibilities and choices, always work towards building self-‐ esteem.
12. TRAINING AND SUPERVISION It is important that all workers understand the agreed procedures for protecting children and/or vulnerable adults. Where possible workers should have clear job descriptions; each worker should have a clear description of their tasks, supervisory arrangements (both of themselves and their responsibility for others) and any guidelines and agreed procedures.
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 151
13. SCHOOLS WORK Local Educational Authorities often ask for those who work with them to provide a DBS (FORMERLY CRB) clearance check. In those cases where the same youth ministries are working with a number of different LEA organisations, we encourage a Trust Agreement to be arranged with the LEA and the YWAM team. This would be an agreement that those who are operating in that team are checked / supervised by DBS (FORMERLY CRB) checked and cleared YWAM staff and therefore it is not necessary to repeat gaining a Disclosure Certificate.
14. OUTREACHES In the event of a YWAM outreach team visiting a location where there is not an active Safeguarding Policy, then YWAM England policy is in operation and needs to be followed.
15. AUDIT The implementation of this policy will be audited in the following ways: • Workers directly involved with children and young people and/or vulnerable adults will attend a regular meeting to discuss policy and practice issues. • All YWAM staff, volunteers and trainees will attend an annual training session on safeguarding. • A register will be maintained of all workers with whom the Policy has been discussed, and those who have received training. • Random visits by ST or by an outside agency to check on the implementation of policy and practice. • Disclosure and Barring Service (formerly Criminal Records Bureau) checks will be carried out on all staff, volunteers and trainees working directly with children, young people and/or vulnerable adults. This document is based on a model safeguarding policy supplied by the Churches Child Protection Advisory Service -‐ a project of PCCA Child Care. A copy of this policy and all amendments will be filed with CCPAS. This policy must not be copied by other churches/organisations without the written agreement of CCPAS and YWAM-‐England. For further information or resources visit CCPAS at YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 152
APPENDIX A Supplementary Documents to YWAM England Safeguarding Policy These documents should be used alongside YWAM-England’s safeguarding policies and practices. Safeguarding Referral Form – for recording disclosures of alleged abuse and action taken. Self-Disclosure Form – for personal voluntary disclosure of previous offences and giving permission to run Disclosure and Barring Service checks/updates. Short Term Teams Safeguarding Guidelines – brief description of Safeguarding Policy for use with short-‐term teams, with signature panel to return at end. Statement of Adult In Loco Parentis – for YWAM staff taking on temporary parental care of someone under the age of 18 (e.g. 17 year old on DTS) Safeguarding Information for All Staff and Students – Brief description of Safeguarding Policy, with signature panel as proof of annual safeguarding training. Translation Contract – for those deemed trustworthy and of good language skills to complete before translating foreign police checks. Police Check Guide – Current information on YWAM England police check procedures. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 153
Safeguarding Information for All Staff and Students Serving with Youth With A Mission England To be accepted as a student or to serve as staff with Youth With A Mission England you need to read and understand the information below and sign both copies returning one to your school/team leader. Our Values • To safeguard and promote the welfare of children, young people, and vulnerable adults. • To listen to, relate effectively and value children, young people, and vulnerable adults. ABUSE COVERS THE FOLLOWING: Children and young people Physical Abuse The infliction of pain or physical injury, which is either caused deliberately, or through lack of care, which many involve hitting, shaking, throwing, poisoning, burning or otherwise physically harming a child in your care. Sexual Abuse Forcing or enticing a child or young person to take part in sexual activities, whether or not the child is aware of what is happening, with or without physical contact. This includes producing or watching sexual activities and “grooming” Psychological or Emotional Abuse The persistent emotional ill treatment, including rejection, bullying and witnessing the ill treatment of another (e.g. domestic violence) causing severe and persistent adverse effects on a child’s emotional development. Neglect The persistent failure to meet a child’s basic physical and or psychological needs, likely to result in the serious impairment of the child’s health or development; failure to provide adequate food, clothing and shelter, protect from physical and emotional harm/danger; ensure adequate supervision; or ensure access to appropriate medical care. Vulnerable Adults: Physical Abuse YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 154
The infliction of pain or physical injury, which is either caused deliberately, or through lack of care. Sexual Abuse The involvement in sexual activities to which the person has not consented or does not truly comprehend and so cannot give informed consent, or where the other party is in a position of trust, power or authority to override or overcome lack of consent. Psychological or Emotional Abuse Acts or behaviour, which cause mental distress or anguish or negates the wishes of the vulnerable adult. It is also behaviour that has a harmful effect on the vulnerable adults emotional health and development or any other form of mental cruelty. Neglect or Act of Omission The repeated deprivation of assistance that the vulnerable adult needs for important activities of daily living, including the failure to intervene in behaviour which is dangerous to the vulnerable adult or to others. A vulnerable person may be suffering from neglect when their general well being or development is impaired. Financial or Material Abuse The inappropriate use, misappropriation, theft or embezzlement of money, property or possessions. Discriminatory Abuse The inappropriate treatment of a vulnerable adult because of their age, gender, race, religion, cultural background , sexuality, disability ect.. Discriminatory abuse exists when values, beliefs or culture result in a misuse of power that denies opportunity to some groups or individuals. Discriminatory abuse links to all other forms of abuse. YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 155
Young people who sexually abuse A third of sexual offenses against children are carried out by a young person under the age of 18, some of whom will continue as adults to sexually abuse children. It is still considered sexual abuse even if the person committing the abuse is under 18 years of age. Internet Safeguarding Issues When you are on the internet, you are still a YWAMer, so therefore we expect you to engage in safe online relationships with minors who you may come in contact with as a result of your YWAM activities. The Alleged Abuse • Can be current or happened in the past. • Can be a one off incident or recurring over weeks, months or years • Has happened at this location, or elsewhere Guidance and Procedure • If a person tells a student or team member about abuse: • Listen carefully, keep calm, but don’t ask questions. • Take the person seriously. • Never promise to keep it a secret. If an illegal act has occurred it MUST be reported to the police or social services • Reassure the person that they have done the right thing. • Pass on the information to your school/team/base leader as soon as possible. • Write up what you have been told afterwards using the person’s own words and give to one of the Safeguarding Team Officers listed below. • Remember, all that is shared is strictly confidential, between you, the person and the appropriate people indicated below. What happens next? The student or staff member reports immediately to their School/Team/Base Leader. Make sure you know the name of the person who has disclosed the abuse. But do not leave that person alone as they will be in a very vulnerable state having just talked about their experiences. The School/Team/Base Leader will immediately contact one of the Safeguarding Team (ST) who will then be responsible for the matter. For YWAM England this is Rob Hobbs: 07734440594 Serena Baker: 07795 844473 Steve Bishop: 07825 767696 Anne Sloan: 07905 419120. The ST Officer will involve the other members of the Safeguarding Team for their support of the student or staff member involved as required. PLEASE SIGN BOTH COPIES, RETURNING ONE COPY TO THE SCHOOL/TEAM LEADER AND KEEP THE OTHER COPY FOR YOUR REFERENCE. THANK YOU YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 156
SAFEGUARDING DECLARATION I declare I have read and understood the above Safeguarding information and agree to abide by the procedures laid down. Signed: __________________________________Date:__________________________________ Full Name: _____________________________________________________________________
Statement of Adult Acting In Loco Parentis In loco parentis means in the place of a parent or instead of a parent. In order for YWAM to decide that you are acting in loco parentis you must have intentionally taken on the duties of a parent. We consider you as acting in loco parentis when: • The minor / child’s parents are absent • You are not the legal guardian • You have taken over daily care and control of the minor Below are the duties an adult acting in loco parentis will do. By signing this form you are stating that you will carry out the daily care and control of the minor: • Ensure that the minor has basic food, shelter and clothing • Make sure that the minor is attending class or fulfilling required duties • Take the minor to any medical or dental appointments required • Ensure that the minor does not travel alone • Be available in any emergency and if needed during the night • Make decisions in the minor’s best interests in a medical emergency if it is impossible to contact the parents • Always be aware of the minor’s whereabouts at any given time • Make sure the minor knows how to contact you at any given time • Provide guidance and discipline as needed YOUR DETAILS Last name___________________________ First Name_____________________________________ Phone numbers: work_________________home__________________mobile__________________ email___________________________________ Current address_________________________________________________________________ MINOR’S DETAILS Last name______________________________ First name__________________________________ Date of birth_________________________ PARENT’S/ LEGAL GUARDIAN’S DETAILS Parent 1 Last name______________________________ First name___________________________ Phone numbers: work___________________home___________________mobile_______________ Current address____________________________________________________________________ _______________________________________________________________________________ Parent 2 Last name__________________________First name_______________________________ Phone numbers: work_____________________home_________________mobile_______________ YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 157
Current address____________________________________________________________________ __________________________________________________________________________ Legal guardian’s last name______________ First name____________________________________ (if different from parent) Phone numbers: work____________________home______________________mobile___________ Current address____________________________________________________________________ email_________________________ Do you have permission from the minor’s parents/guardian to care for the minor? Yes / no If yes, is it in writing? Yes / no Signature of adult acting in loco parentis ________________________________date_____________ Signature of parent/guardian _________________________________________date_____________
YWAM HARPENDEN STAFF HANDBOOK (Edited April 2013) page 158 | https://issuu.com/ywamharpenden/docs/staff_handbook | CC-MAIN-2017-30 | refinedweb | 54,268 | 60.14 |
Due: Thursday, July 19th, 11AM PST
YEAH Hours: Friday, July 13th, 1:30-2:20PM (Gates B01)
May be done in pairs
Your third assignment is a Snowman game (based on the old "Hangman" game) that will give you practice with methods, strings and file-reading.
There is a starter project including all necessary files that you can access using the link below. Once you have the starter code set up, edit
Snowman.java so that the assignment actually does what it’s supposed to do (see the assignment handout), which will involve a cycle of coding, testing, and debugging until everything works. The final step is to submit your assignment.
This assignment may (optionally) be done in pairs. As a reminder, you may only pair up with others with the same section time and location.
Note: You may only use concepts covered up through lecture on Wednesday, July 11 to solve these problems. In particular, you may not use Java concepts you may have learned previously such as private instance variables, arrays, etc. However, you may use concepts we cover over the next week about graphics for any optional extensions if you would like. If you have any questions about what is ok/not ok to use, please feel free to ask.
To run the demo, download the zip file below and unzip, and double-click the enclosed JAR file to run. If you are unable to run it by double-clicking, right-click on the demo JAR file and click "Open".
If you would like to view them separately, the output files, which are already included in the starter code in the
output folder, are listed below as well for each task specified in the assignment handout.
Note: the "Debugging with Karel" handout still provides valuable debugging tips for Java programs! In particular, the debugger functions identically for Karel and Java programs.
import java.applet.*; the handout has been updated to reflect this.
char?
Stringand do string processing if you would like the first character.
promptUserForFilemethod to ask the user for a file name. No matter what file name I type, it never stops re-prompting me to enter the file name again and again. What is wrong?
Hangman, so I renamed it to my own name such as
DaveIsGreat. That is okay, right? | https://web.stanford.edu/class/archive/cs/cs106a/cs106a.1188/assignments/snowman.html | CC-MAIN-2018-30 | refinedweb | 386 | 71.85 |
DORF -- Implementor's view
The implementation has been prototyped in GHC 7.2.1, see, and SPJ's observations/possible improvements and caveats
A cut-down prototype is attached to this page. (The ugliest hacks removed.).
Option One:!]
fieldLabel is not some new ontology in Haskell, it's only sugar.).-shareing.
For this variation:
data Customer_Order = Cust_Order { customer_id :: Int, order_num :: Int, ... } sharing (customer_id) share (order_num) deriving (...)
The share fields are declared at this point -- generate the Proxy and the (overloadable) field selector.
Pros, compared with Option One or Two:
- No extra declaration style; nor innocuous-looking declaration with unobvious effects
Cons:
- This obscures the approach of declaring a data dictionary first.
- May lead to 'dependency hell' between record types.
- Prevents putting class constraints on the record type argument to the selector function.
- Prevents putting class constraints on the field type result from the function.
Perhaps the data dictionary/dependency hell could be avoided with a dummy record type to declare all the shared fields:
data Customer_fieldLabels = Cust_fLabs{ customer_id :: Int, lastName, firstName :: String, product_id :: Int, ... order_num :: Int, ... } share (All)
(This was a typical kludge on the System/38.).
On the other hand, the advantage of repeating the type (from an implementation point of view) is that the desugarrer doesn't have to look for the fieldLabel to generate the Has instance.
Opportunity for improvement! ]
Record/field update
Update uses method set from the Has class:
set :: (Has r fld t) => fld -> t -> r -> r
set's., .. } } (not r), and the result from set depends only on the record type r (not (and to improve the result from get) -- rather than type family SetResult and Get higer-ranked type is hidden inside HR instance (t ~ ([a_] -> [a_])) => -- same as SORF Has HR Proxy_rev t where get HR{rev} _ = rev -- set _ fn HR{..} = HR{rev = fn, ..} -- compile fails: can't match fn's type to rev's 3 years ago.
Prototype implementation
- DORF Prototype Importing 29Feb2012.lhs (4.9 KB) - added by AntC 3 years ago.
demo importing and namespace control of field clashes
Download all attachments as: .zip | https://ghc.haskell.org/trac/ghc/wiki/Records/DeclaredOverloadedRecordFields/ImplementorsView?version=21 | CC-MAIN-2015-18 | refinedweb | 348 | 64.2 |
Sunday, December 9, 2007
Free ZODB!?
Monday, November 5, 2007
New release of Epigrass coming soon!...
Friday, September 21, 2007
The Wonders of Pyglet
The most important feature of Pyglet is that it's being designed from the ground up to be OS independent (Linux, Win, OSX) without external dependencies. For that, it uses the standard OpenGL implementation of each of these platforms via ctypes. This makes it my last best hope for a multi-platform graphical interface kit.
It already has a growing widget library, support for layout of html documents, import 3d models created with wings3d, a scene 2d module with support to sprites and collision detection, and a lot more. Most of these functionalities are available only in the SVN version. The (stable) release is somewhat more limited.
Go check it out! it is (IMHO) one of the few truly exciting graphical libraries in the python scene.
Monday, September 17, 2007
Parallel Processing in CPython
Before I go on, the usual disclaimer: I know that PP does multi-processing, not multi-threading, which is what the GIL won't let you do. But PP offers a very simple and intuitive API, that can be used for both multi-core CPUs and clusters. If, after seeing what PP can do for you, you still believe you need threads, use Jython!!
All examples here were run on a Xeon quad core, with 4GB of RAM, Running Ubuntu Feisty. Python interpreters used were: CPython 2.5.1, Jython 2.1 on java 1.6.0 and IronPython 1.0.2467.
Let's start with Parallel Python: I am using an example taken straight from PP's web site. Here is the code:
#!/usr/bin/python
# File: dynamic_ncpus.py
# Author: Vitalii Vanovschi
# Desc: This program demonstrates parallel computations with pp module
# and dynamic cpu allocation feature.
# Program calculates the partial sum 1-1/2+1/3-1/4+1/5-1/6+... (in the limit it is ln(2))
# Parallel Python Software:
import math, sys, md5, time
import pp
def part_sum(start, end):
"""Calculates partial sum"""
sum = 0
for x in xrange(start, end):
if x % 2 == 0:
sum -= 1.0 / x
else:
sum += 1.0 / x
return sum
print """Using Parallel Python"""
start = 1
end = 20000000
# Divide the task into 64 subtasks
parts = 64
step = (end - start) / parts + 1
# Create jobserver
job_server = pp.Server()
# Execute the same task with different amount of active workers and measure the time
for ncpus in (1, 2, 4, 8, 16, 1):
job_server.set_ncpus(ncpus)
jobs = []
start_time = time.time()
print "Starting ", job_server.get_ncpus(), " workers"
for index in xrange(parts):
starti = start+index*step
endi = min(start+(index+1)*step, end)
# Submit a job which will calculate partial sum
# part_sum - the function
# (starti, endi) - tuple with arguments for part_sum
# () - tuple with functions on which function part_sum depends
# () - tuple with module names which must be imported before part_sum execution
jobs.append(job_server.submit(part_sum, (starti, endi)))
# Retrieve all the results and calculate their sum
part_sum1 = sum([job() for job in jobs])
# Print the partial sum
print "Partial sum is", part_sum1, "| diff =", math.log(2) - part_sum1
print "Time elapsed: ", time.time() - start_time, "s"
job_server.print_stats()
and here are the results:
Using Parallel Python
Starting 1 workers Partial sum is 0.69314720556 | diff = -2.50000421476e-08 Time elapsed: 7.85552501678 s
Starting 2 workers Partial sum is 0.69314720556 | diff = -2.50000421476e-08 Time elapsed: 4.37666606903 s
Starting 4 workers Partial sum is 0.69314720556 | diff = -2.50000421476e-08 Time elapsed: 2.11173796654 s Starting 8 workers Partial sum is 0.69314720556 | diff = -2.50000421476e-08 Time elapsed: 2.06818294525 s
Starting 16 workers Partial sum is 0.69314720556 | diff = -2.50000421476e-08 Time elapsed: 2.06896090508 s
Starting 1 workers Partial sum is 0.69314720556 | diff = -2.50000421476e-08 Time elapsed: 8.11736106873 s Job execution statistics: job count | % of all jobs | job time sum | time per job | job server 384 | 100.00 | 67.1039 | 0.174750 | local Time elapsed since server creation 27.0066168308
In order to compare it to threading code, I had to adapt the example to use threads. Before I fed the new code to Jython, I ran it though CPython to illustrate the fact that, under the GIL, threads are not executed in parallel but one at a time. This first run would also serve as a baseline to compare Jython results against.
The code is below. Since Jython 2.1 does not have the sum function, I implemented it with reduce (there was not perceptible perfomance difference when compared with the built-in sum).
#jython threads
import math, sys, time
import threading
global psums
def part_sum(start, end):
"""Calculates partial sum"""
sum = 0
for x in xrange(start, end):
if x % 2 == 0:
sum -= 1.0 / x
else:
sum += 1.0 / x
psums.append(sum)
def sum(seq):
# no sum in Jython 2.1, we will use reduce
return reduce(lambda x,y:x+y,seq)
print """Using: jython with threading module"""
start = 1
end = 20000000
# Divide the task into 64 subtasks
parts = 64
step = (end - start) / parts + 1
for ncpus in (1, 2, 4, 8, 16,1):
# Divide the task into n subtasks
psums = []
parts = ncpus
step = (end - start) / parts + 1
jobs = []
start_time = time.time()
print "Starting ",ncpus, " workers"
for index in xrange(parts):
starti = start+index*step
endi = min(start+(index+1)*step, end)
# Submit a job which will calculate partial sum
# part_sum - the function
# (starti, endi) - tuple with arguments for part_sum
t=threading.Thread(target=part_sum,name="", args=(starti, endi))
t.start()
jobs.append(t)
# wait for threads to finish
[job.join() for job in jobs]
# Retrieve all the results and calculate their sum
part_sum1 = sum(psums)
# Print the partial sum
print "Partial sum is", part_sum1, "| diff =", math.log(2) - part_sum1
print "Time elapsed: ", time.time() - start_time, "s"
and here are the results for CPython:
Using: CPython with threading module
Starting 1 workers
Partial sum is 0.69314720556 | diff = -2.50001152002e-08
Time elapsed: 8.17702198029 s
Starting 2 workers
Partial sum is 0.69314720556 | diff = -2.50001570556e-08
Time elapsed: 10.2990288734 s
Starting 4 workers
Partial sum is 0.69314720556 | diff = -2.50001127577e-08
Time elapsed: 11.1099839211 s
Starting 8 workers
Partial sum is 0.69314720556 | diff = -2.50001097601e-08
Time elapsed: 11.6850161552 s
Starting 16 workers
Partial sum is 0.69314720556 | diff = -2.50000701252e-08
Time elapsed: 11.8062999249 s
Starting 1 workers
Partial sum is 0.69314720556 | diff = -2.50001152002e-08
Time elapsed: 11.0002980232 s
Here are the results for Jython:
Using: jython with threading module
Starting 1 workers
Partial sum is 0.6931472055600734 | diff = -2.500012807882257E-8
Time elapsed: 4.14300012588501 s
Starting 2 workers
Partial sum is 0.6931472055601045 | diff = -2.500015916506726E-8
Time elapsed: 2.0239999294281006 s
Starting 4 workers
Partial sum is 0.6931472055600582 | diff = -2.5000112868767133E-8
Time elapsed: 2.1430001258850098 s
Starting 8 workers
Partial sum is 0.6931472055600544 | diff = -2.500010909400885E-8
Time elapsed: 1.6349999904632568 s
Starting 16 workers
Partial sum is 0.6931472055600159 | diff = -2.5000070569269894E-8
Time elapsed: 1.2360000610351562 s
Starting 1 workers
Partial sum is 0.6931472055600734 | diff = -2.500012807882257E-8
Time elapsed: 2.4539999961853027 s
And lastly, the results for IronPython:
Using: IronPython with threading module
Starting 1 workers
Partial sum is 0.6931472055601 | diff = -2.50001280788e-008
Time elapsed: 13.6127243042 s
Starting 2 workers
Partial sum is 0.6931472055601 | diff = -2.50001591651e-008
Time elapsed: 7.60165405273 s
Starting 4 workers
Partial sum is 0.6931472055601 | diff = -2.50001128688e-008
Time elapsed: 8.14302062988 s
Starting 8 workers
Partial sum is 0.6931472055601 | diff = -2.5000109205e-008
Time elapsed: 8.32349395752 s
Starting 16 workers
Partial sum is 0.6931472055600 | diff = -2.50000707913e-008
Time elapsed: 8.37589263916 s
Starting 1 workers
Partial sum is 0.6931472055601 | diff = -2.50001280788e-008
Time elapsed: 10.3567276001 s
Now on to some final considerations. The quality of a parallelization tool should be measured not in how fast it is, but how well it scales. The attentive reader may have noticed that Jython threads, were twice as fast than PP. But is that performance related to the threads? No, since it was already faster than CPython (with threading or with PP) for a single thread. PP scaled better up to the available number of Cores, consistently halving the time when doubling the number of cores used. Jython, halved the time when it went from one to two threads, but failed to halve the time again, when going to 4 threads. I'll give it a break here since it recovered at 8 and 16 threads.
Threads alone are not the answer, if they are not well implemented. Look at the results from IronPython, It seem not to be able to take advantage of more than two threads, on a four core system. Can anyone explain this? I'd be curious to know why.
Wednesday, September 12, 2007
ZODB vs Durus
>>IMAGE()
Tuesday, September 11, 2007
ZODB vs Relational Database: a simple benchmark
Since_1<<!
Monday, September 3, 2007
PyconBrasil[03]
Last.
Friday, August 24, 2007
First Course of Scientific Python was a success!
The.
Monday, August 6, 2007
Set implementation performance. | http://pyinsci.blogspot.in/2007/ | CC-MAIN-2018-09 | refinedweb | 1,531 | 78.65 |
Dear Reader,
We all know that Ruby is dynamic language where in calling a method on a type or perhaps object in ruby is not known or figured out until run time.
So assume that if your writing your class and if some one else is accessing your class and tries to call some method in your class, which may have been removed or modified or not at all exists and unfortunately the API document has not be assumed, then at run time ruby throws an exception called NoMethodError.
Although the above said problem/issue might sound not so important to you, but think in a large-scale enterprise application where in your dealing with a lot of classes and you may some times forget to fix every thing or some one might have done the same. So rather than having exceptions at run time and making it a show stopper bug you can write some safety net in your class code or in your project and making the whole app a bit more safer to work with.
Today i learned this part of the topic and i hope you find it useful too as i did and i actually liked it too. So let me start by showing you a small code where there is no safety net implemented:
class MyClass
def SomeMethod
end
def SomeOtherMethod
end
end
MyClass.new.SomeOnesMethod
The above code will not display any problem when you build your project (i tried in netbeans, and no errors) but when you execute it you get exceptions thrown by ruby as “NoMethodError”.
To overcome this problem or in other words to implement a safety net, you need to override Kernel.method_missing(symbol, *args) method in your class, below image shows the intellisense on the same:
So upon implementing this method in the above code, i pretty much do not get any NoMethodError exceptions at run time, below code shows the same:
class MyClass
def SomeMethod
end
def SomeOtherMethod
end
def method_missing(symbol, *args)
puts “Method name = #{symbol} is not present or missing with arguments #{args.inspect}”
end
end
MyClass.new.SomeRandomMethod(1,2,3)
Output: Method name= SomeOnesMethod is not present or missing with arguments [1, 2, 3]
So as you can see, the above code gives a normal output without any exception at all. So my application having this code is much safer now.
Allow me to explain the method_missing() method signature. The first argument symbol is a code block which gets the method name in it, if i can relate to C# .NET, then its some thing like delegates. The second argument gets all the arguments passed to a method from caller side, actually the * prefixed to it denotes that it’s an array type which can accept 1 or more number of arguments. In the body of this method_missing() method, i am using Interpolation technique to print Symbol value and same with args array.
Happy Coding 🙂
P.S: Your valuable comments/votes are appreciated 🙂 | https://adventurouszen.wordpress.com/2011/10/28/safe-guarding-from-nomethoderror-exception-in-ruby/ | CC-MAIN-2018-05 | refinedweb | 500 | 62.51 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.