issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 261k ⌀ | issue_title stringlengths 1 925 | issue_comments_url stringlengths 56 81 | issue_comments_count int64 0 2.5k | issue_created_at stringlengths 20 20 | issue_updated_at stringlengths 20 20 | issue_html_url stringlengths 37 62 | issue_github_id int64 387k 2.46B | issue_number int64 1 127k |
|---|---|---|---|---|---|---|---|---|---|
[
"weidai11",
"cryptopp"
] | ### Crypto++ Issue Report
* State the operating system and version (Ubutnu 17 x86_64, Windows 7 Professional x64, etc)
Red Hat Enterprise Linux Server release 7.7 (Maipo)
* State the version of the Crypto++ library (Crypto++ 7.0, Master, etc)
Master
* State how you built the library (Makefile, Cmake, distro,... | Failure to set CRYPTOPP_CXX17_EXCEPTIONS with clang | https://api.github.com/repos/weidai11/cryptopp/issues/960/comments | 7 | 2020-07-21T10:55:46Z | 2020-09-09T04:43:01Z | https://github.com/weidai11/cryptopp/issues/960 | 662,878,786 | 960 |
[
"weidai11",
"cryptopp"
] | I tested ecies decrypt api 10000 times, Cryptopp(c++) takes about 10s, Bouncy Castle(java) takes about 3s, eciespy(python) takes about 3s
I tested RSA decrypt api 10000 times, Cryptopp takes about 10s, Bouncy Castle takes about 10s
Does the decrypt api of ecies can be optimized? | When using ECIES to decrypt, cryptopp takes longer to calculate than Bouncy Castle | https://api.github.com/repos/weidai11/cryptopp/issues/959/comments | 1 | 2020-07-18T08:54:41Z | 2020-07-18T16:22:27Z | https://github.com/weidai11/cryptopp/issues/959 | 660,017,751 | 959 |
[
"weidai11",
"cryptopp"
] | Sample code:
```
std::string EncodeDesString(std::string plain)
{
BYTE desKey[] = { ... };
ECB_Mode<DES>::Encryption e;
e.SetKey((const unsigned char *)desKey, DES::KEYLENGTH);
std::string cipher;
try
{
StringSource ss(plain, true,
new CryptoPP::StreamTransformationFilter(e, new He... | des enncode and decode is not equal | https://api.github.com/repos/weidai11/cryptopp/issues/958/comments | 2 | 2020-07-11T07:06:45Z | 2020-07-16T12:59:34Z | https://github.com/weidai11/cryptopp/issues/958 | 655,152,791 | 958 |
[
"weidai11",
"cryptopp"
] | Hi, guys having a problem when cross-compiling for WindowsStore (UWP) ARM64. The compiler shows the error shown below. Even if I create an empty file, which only includes the `pch.h` and the `arm_simd.h` files - it fails. I tried moving the `VEXT_U8` function from the `arm_simd.h` to the empty source file (this time wi... | [arm_simd.h] Failed to cross-compile from x64 to ARM64 | https://api.github.com/repos/weidai11/cryptopp/issues/955/comments | 2 | 2020-06-19T07:02:37Z | 2021-02-03T18:19:43Z | https://github.com/weidai11/cryptopp/issues/955 | 641,754,356 | 955 |
[
"weidai11",
"cryptopp"
] | The code below is essentially the same as the example at https://www.cryptopp.com/wiki/GCM_Mode#AEAD except that the tag size is configurable using a compiler define.
The following anomalies were observed with fuzz testing:
- Compile with ```-DTAG_SIZE=32``` to observe that encryption succeeds, but subsequent dec... | AES GCM encryption with large tag size results in incorrect output, out-of-bounds reads | https://api.github.com/repos/weidai11/cryptopp/issues/954/comments | 2 | 2020-06-08T11:48:38Z | 2020-12-20T00:53:20Z | https://github.com/weidai11/cryptopp/issues/954 | 634,540,201 | 954 |
[
"weidai11",
"cryptopp"
] | VectorSource and/or VectorSink cannot compile when passed a vector that takes a custom allocator.
In my case I have a codebase that uses a secure allocator for all sensitive information and have to re-implement parts of the cryptopp codebase due to VectorSource/VectorSink not taking an allocator.
VectorSink is just... | Custom allocators for VectorSink/VectorSource | https://api.github.com/repos/weidai11/cryptopp/issues/953/comments | 2 | 2020-06-08T10:56:17Z | 2020-07-13T12:20:31Z | https://github.com/weidai11/cryptopp/issues/953 | 634,507,505 | 953 |
[
"weidai11",
"cryptopp"
] | I use Crypto++ to calculate HMAC-SHA256 signature. My code is similar to this one:
```cpp
#include <string>
#include <string_view>
#include <cryptopp/filters.h>
using CryptoPP::StringSink;
using CryptoPP::StringSource;
using CryptoPP::HashFilter;
#include <cryptopp/hmac.h>
using CryptoPP::HMAC;
#inclu... | Header and source files dependencies | https://api.github.com/repos/weidai11/cryptopp/issues/951/comments | 2 | 2020-06-02T00:49:16Z | 2020-12-17T19:38:35Z | https://github.com/weidai11/cryptopp/issues/951 | 628,820,089 | 951 |
[
"weidai11",
"cryptopp"
] | Please, see https://github.com/cryfs/cryfs/issues/345 | Can't compile on Android due to wrong evaluation of CRC support | https://api.github.com/repos/weidai11/cryptopp/issues/950/comments | 24 | 2020-05-21T22:05:42Z | 2021-06-11T13:25:51Z | https://github.com/weidai11/cryptopp/issues/950 | 622,819,469 | 950 |
[
"weidai11",
"cryptopp"
] | - Cryptopp version 8.2.0 release version downloaded from github release
- MAC OS: Catalina Version 10.15.4
Following the exact steps from documentation but end up having errors

{
const uint8_t key[3] = { 0 };
::CryptoPP::SipHash<2, 4, false> siphash(key, sizeof(key));
return 0;
}
```
I think it would be more appropriate to throw an exception in this case? | Undersized SipHash key leads to buffer out-of-bounds read | https://api.github.com/repos/weidai11/cryptopp/issues/947/comments | 2 | 2020-05-04T16:21:45Z | 2020-12-20T00:55:37Z | https://github.com/weidai11/cryptopp/issues/947 | 612,001,592 | 947 |
[
"weidai11",
"cryptopp"
] | The use of `std::uncaught_exception` has been deprecated in favour of `std::uncaught_exceptions` (note extra 's'). https://en.cppreference.com/w/cpp/error/uncaught_exception
I can do a quick PR for this. I guess it would need to switch based on the C++ language version (17 and later using the new API). I've not look... | Use of uncaught_exception | https://api.github.com/repos/weidai11/cryptopp/issues/946/comments | 3 | 2020-04-26T06:21:54Z | 2020-04-28T07:47:33Z | https://github.com/weidai11/cryptopp/issues/946 | 606,932,141 | 946 |
[
"weidai11",
"cryptopp"
] | Reproducer:
```cpp
#include <modes.h>
#include <filters.h>
#include <speck.h>
#define CF_CHECK_EQ(expr, res) if ( (expr) != (res) ) { goto end; }
std::vector<uint8_t> Encrypt(const std::vector<uint8_t>& key, const std::vector<uint8_t>& iv, const std::vector<std::vector<uint8_t>>& cleartext) {
::CryptoP... | SPECK64 different output if input is passed in chunks | https://api.github.com/repos/weidai11/cryptopp/issues/945/comments | 8 | 2020-04-22T23:12:05Z | 2020-12-20T00:55:52Z | https://github.com/weidai11/cryptopp/issues/945 | 605,130,480 | 945 |
[
"weidai11",
"cryptopp"
] | The executive summary is:
* Ubuntu 18.04
* Current master from test fork
* Autoconf
./configure --prefix='/home/sjmunroe/work/test/install' CFLAGS='-m64 -O3 -g0 -mcpu=power9' CXXFLAGS='-m64 -O3 -g0 -mcpu=power9' CPPFLAGS="-DNDEBUG" LDFLAGS='-m64 -Wl,-q'
make
The build configure is NOT cleanly propagating the... | Problems builing Crypto++ for POWER9 | https://api.github.com/repos/weidai11/cryptopp/issues/944/comments | 3 | 2020-04-21T00:11:50Z | 2020-06-04T01:09:32Z | https://github.com/weidai11/cryptopp/issues/944 | 603,614,013 | 944 |
[
"weidai11",
"cryptopp"
] | Debian reports self test failures for K233 on Power8. We can also duplicate it on GCC111 with XL C++ compiler. This appears to be related to polynomial multiply code.
```
Testing SEC 2 EC2N curves...
passed 163 bits
passed 163 bits
passed 239 bits
passed 113 bits
passed 113 bits
passed 163... | K233 failure on Power8 | https://api.github.com/repos/weidai11/cryptopp/issues/943/comments | 0 | 2020-04-10T18:44:30Z | 2020-04-10T18:44:30Z | https://github.com/weidai11/cryptopp/issues/943 | 598,035,201 | 943 |
[
"weidai11",
"cryptopp"
] | [Cirrus CI](https://cirrus-ci.org/) provides FreeBSD images for testing. This report will track the addition of Cirrus CI integration.
The BSDs have a personality distinct from Linux. To date our testing is manual. On occasion we fire up our DragonFly, FreeBSD, NetBSD and OpenBSD virtual machines and test a build. I... | Add Cirrus CI testing | https://api.github.com/repos/weidai11/cryptopp/issues/940/comments | 1 | 2020-03-24T18:00:22Z | 2020-12-20T00:56:10Z | https://github.com/weidai11/cryptopp/issues/940 | 587,169,851 | 940 |
[
"weidai11",
"cryptopp"
] | As per 5.6.4 version Crypto++ supported CMake, however, in the current version CMakeLists.txt is not available.
CMake is an industry standard, and most of build systems use it. The most excluding it affects solutions which attempt to upgrade to a newer version of Crypto++, causing deadlines delay and forcing to use ol... | CMake-based build toolchain | https://api.github.com/repos/weidai11/cryptopp/issues/939/comments | 2 | 2020-03-18T13:49:10Z | 2024-03-28T22:04:53Z | https://github.com/weidai11/cryptopp/issues/939 | 583,741,981 | 939 |
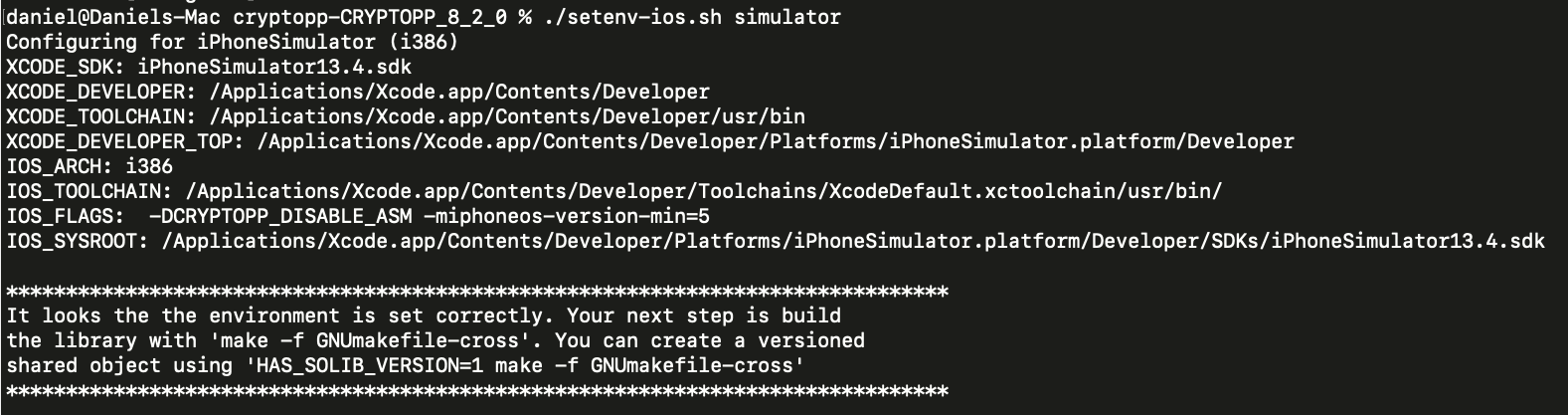
[
"weidai11",
"cryptopp"
] | Our scripts to build Android and iOS are stale. We need to update them.
This issue report will track the changes. | Update Android and iOS builds | https://api.github.com/repos/weidai11/cryptopp/issues/936/comments | 0 | 2020-03-09T13:56:11Z | 2020-12-20T00:56:30Z | https://github.com/weidai11/cryptopp/issues/936 | 577,927,588 | 936 |
[
"weidai11",
"cryptopp"
] | ### Crypto++ Issue Report
* The operating system and version (Centos7 x86_64, Windows 10 Professional x64, etc)
* The version of the Crypto++ library (The latest Crypto++ 8.20)
* How you built the library (Makefile, Cmake, Visual Studio 2017)
I'd like to use Crypto++ in my project. And there will be two output re... | Is there any document on how to use Crypto++ library ? | https://api.github.com/repos/weidai11/cryptopp/issues/935/comments | 2 | 2020-02-29T11:15:23Z | 2021-02-03T18:29:07Z | https://github.com/weidai11/cryptopp/issues/935 | 573,275,970 | 935 |
[
"weidai11",
"cryptopp"
] | I am compiling CryptoPP with 3rd party library. And, it happens to have macro Divide, that is defined in CryptoPP as well. Fortunately, one had 4 parameters, other 5, and failing compile. Otherwise I would die to find what is wrong - code would compile but use wrong macro from another library.
I have non-trivial imp... | Macro name conflict with 3rd party library | https://api.github.com/repos/weidai11/cryptopp/issues/934/comments | 2 | 2020-02-28T16:53:47Z | 2020-03-02T00:40:13Z | https://github.com/weidai11/cryptopp/issues/934 | 572,873,607 | 934 |
[
"weidai11",
"cryptopp"
] | ### Crypto++ Issue Report
Thanks for taking the time to report an issue. Reporting issues helps us improve stability and reliability for all users, so it is a valuable contribution.
Please do not ask questions in the bug tracker. Please ask questions on the Crypto++ Users List at http://groups.google.com/forum/#!... | Build fails for iOS | https://api.github.com/repos/weidai11/cryptopp/issues/933/comments | 5 | 2020-02-23T09:36:32Z | 2021-02-03T18:29:24Z | https://github.com/weidai11/cryptopp/issues/933 | 569,467,944 | 933 |
[
"weidai11",
"cryptopp"
] | Hello,
i am new to cryptopp and currently getting familiar with the lib. I am testing with the speck cipher and want to reproduce the example from the wiki shown here:
https://www.cryptopp.com/wiki/SPECK
I am refering to the following lines on the wiki:
Key: F36D4289293A07A0C1E3D8EAFBF83C6F
IV: 50650B834D6... | Speck implemententation not matching test vector from wiki | https://api.github.com/repos/weidai11/cryptopp/issues/932/comments | 4 | 2020-02-09T15:59:11Z | 2020-12-20T00:57:51Z | https://github.com/weidai11/cryptopp/issues/932 | 562,197,861 | 932 |
[
"weidai11",
"cryptopp"
] | Details here:
https://github.com/Entware/Entware/issues/412
Any help would be welcome! | Illegal instruction in CryptoPP::CPU_ProbeARMv7() under armv5tel architecture | https://api.github.com/repos/weidai11/cryptopp/issues/931/comments | 2 | 2020-02-09T14:49:45Z | 2020-02-09T15:17:01Z | https://github.com/weidai11/cryptopp/issues/931 | 562,187,743 | 931 |
[
"weidai11",
"cryptopp"
] | Wiki documentation error in 8.2.0. [GCM Mode](https://www.cryptopp.com/wiki/GCM_Mode) states:
```
byte iv[ AES::BLOCKSIZE * 16 ];
```
Should be:
```
byte iv[ AES::BLOCKSIZE ];
```
This apparent typo confused me since the referenced zip file is also different in several ways and uses the number 12. Note `A... | GCM wiki documentation error/inconsistency with regard to: iv size in bytes. | https://api.github.com/repos/weidai11/cryptopp/issues/930/comments | 4 | 2020-02-07T23:30:35Z | 2020-02-11T18:42:14Z | https://github.com/weidai11/cryptopp/issues/930 | 561,923,612 | 930 |
[
"weidai11",
"cryptopp"
] | ### Crypto++ Issue Report
* OS:
+ Host: Xubuntu: Linux 5.3.0-26-generic #28~18.04.1-Ubuntu SMP Wed Dec 18 16:40:14 UTC 2019 x86_64 x86_64 x86_64 GNU/Linux
+ Target: Android 24, NDK 21.0.6113669
* Crypto++ 8.2.0
* Build script based on setenv-android.sh: [build_crypto++_android.sh](https://github.com/weid... | error caused by cpu-features.c getting compiled with CXX | https://api.github.com/repos/weidai11/cryptopp/issues/926/comments | 1 | 2020-01-28T14:38:28Z | 2020-02-08T16:47:32Z | https://github.com/weidai11/cryptopp/issues/926 | 556,252,766 | 926 |
[
"weidai11",
"cryptopp"
] | AMD cpu's from family 15h and 16h fail to produce random numbers using RDRAND after a suspend/resume. While first reported in 2014, AMD did not diagnose and offer a patch until late 2019. Also see the following bug reports and patches.
Kernel bug:
* https://bugzilla.kernel.org/show_bug.cgi?id=85911
Systemd bug... | Disable RDRAND and RDSEED on AMD cpu's with family 15h or 16h | https://api.github.com/repos/weidai11/cryptopp/issues/924/comments | 1 | 2020-01-17T05:02:17Z | 2020-12-20T00:58:49Z | https://github.com/weidai11/cryptopp/issues/924 | 551,200,630 | 924 |
[
"weidai11",
"cryptopp"
] | I may have found some collisions in BLAKE2b-32 and they are listed below.
**Data:0x13A50A7FCDCF49DFE5
Hash:0x12345678
Data:0x4B10E44FD2
Hash:0x1234567B
Data:0xAAD63D4CF4
Hash:0x12345678
Data:0xF47560ED9C
Hash:0x12345678** | BLAKE2b Collision | https://api.github.com/repos/weidai11/cryptopp/issues/923/comments | 1 | 2020-01-15T05:37:58Z | 2020-01-17T06:41:07Z | https://github.com/weidai11/cryptopp/issues/923 | 549,977,357 | 923 |
[
"weidai11",
"cryptopp"
] | The readme mentions compatibility for Visual Studio 2003 - 2017.
Yet the readme sports instructions for compiling MSVC 2003 - 2015.
Moreover, the site (https://www.cryptopp.com/) mentions compatibility up to 2019.
My immediate question is: Are the compilation instructions valid for 2017? | MSVC version documentation inconsistencies | https://api.github.com/repos/weidai11/cryptopp/issues/922/comments | 1 | 2020-01-08T23:00:57Z | 2020-01-09T01:47:26Z | https://github.com/weidai11/cryptopp/issues/922 | 547,152,469 | 922 |
[
"weidai11",
"cryptopp"
] | Crypto++ 8.2 has a bug in its Blake2b implementation. The output digest values are the same whether a salt is used or not.
I changed the test code in validat5.cpp:2149 to verify this. Passing in a salt doesn't have any effect on the output digest. I used the pyblake2 module to verify that the digest values should be ... | Blake2b implementation: Salt has no effect and produces an incorrect digest. | https://api.github.com/repos/weidai11/cryptopp/issues/921/comments | 2 | 2020-01-05T20:30:09Z | 2020-01-10T05:28:50Z | https://github.com/weidai11/cryptopp/issues/921 | 545,463,092 | 921 |
[
"weidai11",
"cryptopp"
] | Using Cryptopp 8.2, building with setenv-android-gcc.sh on android NDK r20 failed.
Environment
Ubuntu(WSL)
Android SDK with NDK r20.
Looks like the latest ndk changes directories, the setenv-android-gcc.sh is unable to set properly. | Build failed for android NDK r20 | https://api.github.com/repos/weidai11/cryptopp/issues/920/comments | 1 | 2020-01-04T12:19:49Z | 2020-12-20T00:59:09Z | https://github.com/weidai11/cryptopp/issues/920 | 545,278,766 | 920 |
[
"weidai11",
"cryptopp"
] | The Ethereum network recently went through a hardfork which allows users to call the Blake2b compression function `F` directly in their smart contracts (to offer better interoperability with ZCash network). See details of the EIP here, including a link to the specification of the function `F` in question: https://eips.... | Expose Blake2b Compression function for Ethereum Clients | https://api.github.com/repos/weidai11/cryptopp/issues/917/comments | 7 | 2019-12-05T19:03:38Z | 2023-10-02T06:56:18Z | https://github.com/weidai11/cryptopp/issues/917 | 533,536,388 | 917 |
[
"weidai11",
"cryptopp"
] | > I think the original Tiger hash had a padding bug. I think the authors fixed it in a revision.
>
> See [Tiger: A Fast New Cryptographic Hash Function](http://www.cs.technion.ac.il/~biham/Reports/Tiger/). And [Ross Anderson's homepage](https://www.cl.cam.ac.uk/~rja14/), where the two implementations are provided.
... | Tiger official test vectors fail | https://api.github.com/repos/weidai11/cryptopp/issues/916/comments | 1 | 2019-12-01T09:13:27Z | 2019-12-14T00:29:51Z | https://github.com/weidai11/cryptopp/issues/916 | 530,698,913 | 916 |
[
"weidai11",
"cryptopp"
] | OS = Windows 10 x64
Compiler = Visual Studio 2017
Version = CryptoPP v8.2.0
I created my own independent implementation for the Tiger hash on Windows with Visual Studio. Unfortunately, it fails some of the test vectors. I compiled and ran the ValidateTiger() function of CryptoPP v8.2.0 with some of the official te... | Tiger official test vectors fail | https://api.github.com/repos/weidai11/cryptopp/issues/915/comments | 2 | 2019-11-30T21:29:57Z | 2019-12-01T09:05:25Z | https://github.com/weidai11/cryptopp/issues/915 | 530,632,481 | 915 |
[
"weidai11",
"cryptopp"
] | I'm working on an embedded security device, and I have to remove all software-based pseudo-randomness generators. I have removed three so far:
(1) The Intel Rdrand engine inside OpenSSL
(2) The DBRG randomness generator built into OpenSSL
(3) The simulator engine for the TPM2 chip
There's only one software rand... | Compiler flag to omit the PRNG | https://api.github.com/repos/weidai11/cryptopp/issues/914/comments | 1 | 2019-11-20T11:55:11Z | 2019-12-01T00:30:53Z | https://github.com/weidai11/cryptopp/issues/914 | 525,757,044 | 914 |
[
"weidai11",
"cryptopp"
] |
I'm working on a embedded Linux project, using "Buildroot" to put my operating system together along with packages. Buildroot comes with loads of packages already built-in, but it also gives you the option of adding in your own.
I have added libcryptopp to my Buildroot. Before doing this, I searched the web to see... | Two files for Buildroot: Config.in, libcryptopp.mk | https://api.github.com/repos/weidai11/cryptopp/issues/913/comments | 1 | 2019-11-19T13:05:59Z | 2019-12-01T00:50:29Z | https://github.com/weidai11/cryptopp/issues/913 | 524,997,455 | 913 |
[
"weidai11",
"cryptopp"
] | Looks like wiki is down. I get this:
```
Sorry! This site is experiencing technical difficulties.
Try waiting a few minutes and reloading.
(Cannot access the database)
Backtrace:
#0 /var/www/html/w/includes/libs/rdbms/loadbalancer/LoadBalancer.php(769): Wikimedia\Rdbms\LoadBalancer->reportConnectionError(... | https://cryptopp.com/wiki/ fails to load | https://api.github.com/repos/weidai11/cryptopp/issues/911/comments | 3 | 2019-11-05T06:46:48Z | 2019-11-07T17:23:14Z | https://github.com/weidai11/cryptopp/issues/911 | 517,578,075 | 911 |
[
"weidai11",
"cryptopp"
] | Does crypto++ provide an implementation of paillier encryption? | Does crypto++ provide an implementation of paillier encryption? | https://api.github.com/repos/weidai11/cryptopp/issues/906/comments | 2 | 2019-10-25T05:29:54Z | 2019-10-28T23:44:08Z | https://github.com/weidai11/cryptopp/issues/906 | 512,311,121 | 906 |
[
"weidai11",
"cryptopp"
] | Add XTS block cipher mode of operation | Add XTS block cipher mode of operation | https://api.github.com/repos/weidai11/cryptopp/issues/891/comments | 1 | 2019-10-12T11:13:28Z | 2020-12-20T00:59:36Z | https://github.com/weidai11/cryptopp/issues/891 | 506,173,154 | 891 |
[
"weidai11",
"cryptopp"
] | We have `BytePtr` and `ConstBytePtr` for `std::string` that allows us to easily extract a `byte*`:
```
inline byte* BytePtr(std::string& str)
{
// Caller wants a writeable pointer
CRYPTOPP_ASSERT(str.empty() == false);
if (str.empty())
return NULLPTR;
return reinterpret_cast<byte*>(&str[0]);
}
```
... | Add BytePtr and ConstBytePtr overloads for SecByteBlock | https://api.github.com/repos/weidai11/cryptopp/issues/890/comments | 0 | 2019-10-03T07:39:55Z | 2019-10-03T08:12:54Z | https://github.com/weidai11/cryptopp/issues/890 | 501,903,358 | 890 |
[
"weidai11",
"cryptopp"
] | gcc-9.2.0 in pedantic mode complains about extra semicolons here:
```
keccak.h:104:49: warning: extra ';' [-Wpedantic]
104 | DOCUMENTED_TYPEDEF(Keccak_Final<28>, Keccak_224);
| ^
keccak.h:108:49: warning: extra ';' [-Wpedantic]
108 | DOCUMENTED_TYPEDEF(K... | Tiny issue with extra semicolons and gcc-9.2.0 in pedantic mode | https://api.github.com/repos/weidai11/cryptopp/issues/889/comments | 2 | 2019-10-02T13:03:10Z | 2019-10-04T02:41:16Z | https://github.com/weidai11/cryptopp/issues/889 | 501,475,424 | 889 |
[
"weidai11",
"cryptopp"
] | Hi I can not compile my test program with cryptopp
how I compile
g++ -g3 -O2 -Wall -Wextra -o main main.cpp -l:libcryptopp.a
error
Undefined symbols for architecture x86_64:
"CryptoPP::AlignedDeallocate(void*)", referenced from:
CryptoPP::AllocatorWithCleanup<unsigned long, true>::deallocate(voi... | clang: error: linker command failed with exit code 1 (use -v to see invocation) on MacOS | https://api.github.com/repos/weidai11/cryptopp/issues/887/comments | 0 | 2019-09-30T05:32:16Z | 2019-09-30T09:35:45Z | https://github.com/weidai11/cryptopp/issues/887 | 500,059,465 | 887 |
[
"weidai11",
"cryptopp"
] | While working [Issue 884](https://github.com/weidai11/cryptopp/issues/884) we uncovered a circular dependency between `misc.h` and `secblock.h`. `misc.h` provides `AlignedAllocate`, `AlignedDeallocate` and friends. Including `secblock.h` in `misc.h` for use of `SecByteBlock` caused the allocation functions to be undef... | Circular dependency between misc.h and secblock.h | https://api.github.com/repos/weidai11/cryptopp/issues/885/comments | 1 | 2019-09-28T21:02:18Z | 2019-09-29T06:54:50Z | https://github.com/weidai11/cryptopp/issues/885 | 499,820,767 | 885 |
[
"weidai11",
"cryptopp"
] | On occasion I find a need for X509 certificate support. It is not often, but it arises on occasion. Besides just declaring a stand-alone `X509Certificate`, it would be nice to have a class that integrates a little better with the library. All users can benefit from the support.
I think we can offer a stub for better... | Add Certificate interface | https://api.github.com/repos/weidai11/cryptopp/issues/884/comments | 1 | 2019-09-28T06:51:12Z | 2019-09-28T22:30:38Z | https://github.com/weidai11/cryptopp/issues/884 | 499,735,153 | 884 |
[
"weidai11",
"cryptopp"
] | ### Crypto++ Issue Report
operating system and version - centos 6.6
version of the Crypto++ library : Crypto++ 8.2.0,
Recovered Text after decryption does not match
```
#include <filters.h>
#include <osrng.h>
#include <modes.h>
#include <files.h>
#include <aes.h>
#include <iostream>
#include <string>
... | CFB_Mode_ExternalCipher does not work | https://api.github.com/repos/weidai11/cryptopp/issues/883/comments | 3 | 2019-09-26T21:10:43Z | 2019-09-26T22:27:01Z | https://github.com/weidai11/cryptopp/issues/883 | 499,118,246 | 883 |
[
"weidai11",
"cryptopp"
] |
In Windows XP SP2 or lower
cannot locate program input points GetLogicalProcesserInformation()

| Unable to locate program input point GetLogicalProcesserInformation | https://api.github.com/repos/weidai11/cryptopp/issues/882/comments | 2 | 2019-09-25T15:21:40Z | 2019-09-26T21:36:58Z | https://github.com/weidai11/cryptopp/issues/882 | 498,357,385 | 882 |
[
"weidai11",
"cryptopp"
] | * State the operating system and version (Ubutnu 17 x86_64, Windows 7 Professional x64, etc)
Windows 10 RS5 x64
* State the version of the Crypto++ library (Crypto++ 5.6.5, Master, etc)
Tried on master and 8.1.0
* State how you built the library (Makefile, Cmake, distro, etc)
VS solution
* Show a typical command ... | msvc instant crash in debug build | https://api.github.com/repos/weidai11/cryptopp/issues/881/comments | 1 | 2019-09-10T17:19:03Z | 2019-09-22T03:47:46Z | https://github.com/weidai11/cryptopp/issues/881 | 491,799,992 | 881 |
[
"weidai11",
"cryptopp"
] | `Rijndael::Enc::ProcessAndXorBlock` recurses infinitely under certain combinations of defines.:
- `CRYPTOPP_SSE2_ASM_AVAILABLE` is true
- `CRYPTOPP_X64_MASM_AVAILABLE` is not defined
- `CRYPTOPP_AESNI_AVAILABLE` is not defined
- `CRYPTOPP_DISABLE_RIJNDAEL_ASM` is defined
This causes `if (HasAESNI())` to be ru... | Infinite recursion in rijndael.cpp | https://api.github.com/repos/weidai11/cryptopp/issues/880/comments | 6 | 2019-09-10T10:13:27Z | 2019-09-29T01:43:22Z | https://github.com/weidai11/cryptopp/issues/880 | 491,579,753 | 880 |
[
"weidai11",
"cryptopp"
] | I'm just wondering if there's any appetite for this really. Right now internal headers, public headers, implementation and test files are all piled together into a jumbled mess.
Would it not be much better to clean this up? I'd be happy to help with this effort
I think it would also make things much simpler with ... | Project structure re-organisation | https://api.github.com/repos/weidai11/cryptopp/issues/879/comments | 4 | 2019-09-06T06:17:01Z | 2023-10-02T06:41:55Z | https://github.com/weidai11/cryptopp/issues/879 | 490,150,334 | 879 |
[
"weidai11",
"cryptopp"
] | As reported on the mailing list by Philippe Antoine at [Regression in Elliptic Curve Operation on brainpoolP256r1](https://groups.google.com/d/msg/cryptopp-users/RfAFR3_y1sI/qYH2rTavBQAJ):
```
...
I have been doing differential fuzzing about elliptic curve cryptography with different libraries including cryptopp.
... | Regression in Elliptic Curve Operation on brainpoolP256r1 | https://api.github.com/repos/weidai11/cryptopp/issues/878/comments | 20 | 2019-08-26T22:00:55Z | 2021-01-01T20:01:05Z | https://github.com/weidai11/cryptopp/issues/878 | 485,474,676 | 878 |
[
"weidai11",
"cryptopp"
] | ```
std::string PublicKeyString("MHYwTwYGKw4HAgEBMEUCIQDebUvQDd9UPMmD27BJovZSIgWfexL0SWkfJQPMLsJvMwIgDy/kEthwO6Q+L8XHnzumnEKs+txH8QkQD+M/8u82ql0DIwACIAY6rfW+BTcRZ9QAJovgoB8DgNLJ8ocqOeF4nEBB0DHH");
CryptoPP::ByteQueue queue;
CryptoPP::Base64Decoder decoder(new CryptoPP::Redirector(queue));
decoder.Put((... | ElGamal encryption key Load and BERDecodeErr | https://api.github.com/repos/weidai11/cryptopp/issues/876/comments | 24 | 2019-08-24T04:18:48Z | 2020-12-20T01:00:32Z | https://github.com/weidai11/cryptopp/issues/876 | 484,776,595 | 876 |
[
"weidai11",
"cryptopp"
] | https://github.com/weidai11/cryptopp/blob/8130bd7a2405dbf889b8a0e3baa54ace7b630afc/secblock.h#L208
The condition `size == 0` was already checked five lines above. | Size cannot be zero | https://api.github.com/repos/weidai11/cryptopp/issues/875/comments | 1 | 2019-08-22T20:40:24Z | 2020-12-20T01:00:48Z | https://github.com/weidai11/cryptopp/issues/875 | 484,206,008 | 875 |
[
"weidai11",
"cryptopp"
] | ```cpp
#include <sha.h>
#include <pwdbased.h>
int main(void)
{
unsigned char out[714];
const unsigned char password[8] = { 0 };
const unsigned char salt[8] = { 0 };
::CryptoPP::PKCS5_PBKDF1<::CryptoPP::SHA1> pbkdf1;
pbkdf1.DeriveKey(
out,
sizeof(out),
... | PKCS5_PBKDF1 buffer overflow | https://api.github.com/repos/weidai11/cryptopp/issues/874/comments | 4 | 2019-08-16T09:03:29Z | 2020-12-20T01:00:59Z | https://github.com/weidai11/cryptopp/issues/874 | 481,514,733 | 874 |
[
"weidai11",
"cryptopp"
] | I get a 0xc0000005 in cryptotest.exe in rdrand.cpp:249. Here's what I did:
- downloaded Cryptopp 8.2.0, official release zip https://github.com/weidai11/cryptopp/archive/CRYPTOPP_8_2_0.zip
- opened cryptest.sln in VS2017
- upgraded to latest Windows SDK 10.0.17763.0
- build
- run cryptest.exe
The crash happen... | Exception 0xc0000005 in cryptest using VS2017 | https://api.github.com/repos/weidai11/cryptopp/issues/872/comments | 7 | 2019-08-05T12:49:08Z | 2020-12-20T01:01:14Z | https://github.com/weidai11/cryptopp/issues/872 | 476,840,859 | 872 |
[
"weidai11",
"cryptopp"
] | From a private email by Ján Jančár:
> Message-ID: <93874bd8-653e-33e9-c429-93712c3f30ba@mail.muni.cz>
> Subject: Vulnerability disclosure
> ...
>
> During our research into security of elliptic curve cryptography implementations on smart-cards and in software libraries [1], we have discovered timing leakage ... | Elliptic Curve timing leaks | https://api.github.com/repos/weidai11/cryptopp/issues/869/comments | 9 | 2019-07-26T04:49:09Z | 2020-12-20T11:23:40Z | https://github.com/weidai11/cryptopp/issues/869 | 473,175,638 | 869 |
[
"weidai11",
"cryptopp"
] | ### Crypto++ Issue Report
Cross compiling on ubuntu 18.04 for aarch64 (just armv8-a)
Cryptopp 8.0, built using custom buildsystem
```.sh
aarch64-linux-gnu-g++ -MMD -MF obj/deps/build/cryptlib/cryptlib/crc_simd.o.d -DNDEBUG -I../../../deps/build/cryptlib -Wall -Werror -fopenmp -fno-strict-aliasing -funwind-tab... | CRYPTOPP_ARM_CRC32_AVAILABLE is set even when +crc is not set in march | https://api.github.com/repos/weidai11/cryptopp/issues/868/comments | 16 | 2019-07-24T11:29:29Z | 2019-08-05T08:23:15Z | https://github.com/weidai11/cryptopp/issues/868 | 472,230,486 | 868 |
[
"weidai11",
"cryptopp"
] | Currently the recipe to build `cryptest.exe` hard-codes `libcryptopp.a`. From `GNUmakefile`:
```
cryptest.exe:libcryptopp.a $(TESTOBJS)
$(CXX) -o $@ $(strip $(CXXFLAGS)) $(TESTOBJS) ./libcryptopp.a $(LDFLAGS) $(LDLIBS)
```
Using `libcryptopp.a` is a good engineering decision because it sidesteps [path problem... | Add link-library variable to Makefiles | https://api.github.com/repos/weidai11/cryptopp/issues/866/comments | 1 | 2019-07-21T06:12:15Z | 2019-07-21T07:41:23Z | https://github.com/weidai11/cryptopp/issues/866 | 470,747,193 | 866 |
[
"weidai11",
"cryptopp"
] | * openSUSE Tumbleweed (it's a rolling release)
* armv7l
* Crypto++ 8.2.0
* GNUMakefile
Full compilation log: http://susepaste.org/view//9613298
In short: `-march=armv7-a -mfpu=neon` flags are added to compile selected source files. Linking fails with LTO enabled, because those flags are not specified. | LTO build fails due to missint "-m" flags in linker command | https://api.github.com/repos/weidai11/cryptopp/issues/865/comments | 28 | 2019-07-18T21:04:26Z | 2019-09-27T06:17:58Z | https://github.com/weidai11/cryptopp/issues/865 | 469,988,552 | 865 |
[
"weidai11",
"cryptopp"
] | I compile Crypto++ library source code in CentOS 6, run Linux command to get OS info and version:
```
#uname -a
Linux centos6 2.6.32-431.el6.x86_64 #1 SMP Fri Nov 22 03:15:09 UTC 2013 x86_64 x86_64 x86_64 GNU/Linux
```
[SNIP unneeded by JW]
```
#make
g++ -I/usr/local/mysql/include -I/usr/local/include/cry... | Crypto++ 8.2 and misc.h:94:32: error: missing binary operator before token "0" | https://api.github.com/repos/weidai11/cryptopp/issues/864/comments | 7 | 2019-07-13T18:21:16Z | 2019-07-14T16:18:30Z | https://github.com/weidai11/cryptopp/issues/864 | 467,751,690 | 864 |
[
"weidai11",
"cryptopp"
] | As discussed on Stack Overflow at [Crypto++ and neon_vector_type attribute is not supported for this target using Android NDK?](https://stackoverflow.com/q/56988965/608639). The target is `armeabi`, which is the old armv5 gear. The toolchain is ndk-r16b.
android-ndk-r16b/toolchains/llvm/prebuilt/darwin-x86_64/li... | Android and neon_vector_type attribute is not supported for this target | https://api.github.com/repos/weidai11/cryptopp/issues/863/comments | 1 | 2019-07-11T21:54:30Z | 2020-12-20T01:03:10Z | https://github.com/weidai11/cryptopp/issues/863 | 467,125,232 | 863 |
[
"weidai11",
"cryptopp"
] | `BufferedTransformation` lacks `GetWord64` and `PutWord64`. Also see [StreamTransformationFilter: invalid PKCS #7 block padding found using AES decryption](https://stackoverflow.com/q/56945847/608639) on Stack Overflow.
This issue will track the addition. | Add GetWord64 and PutWord64 | https://api.github.com/repos/weidai11/cryptopp/issues/862/comments | 0 | 2019-07-10T14:04:14Z | 2020-12-20T01:03:21Z | https://github.com/weidai11/cryptopp/issues/862 | 466,329,422 | 862 |
[
"weidai11",
"cryptopp"
] | `AutoSeededX917RNG` can be tricky to use correctly due to `Reseed`. If user input is too small or seed size is too large then uninitialized data could be used to key the underlying block cipher. Feeding uninitialized data to the RNG is not necessarily a bad thing since entropy is a good thing. However, we should probab... | Use HKDF in AutoSeededX917RNG::Reseed | https://api.github.com/repos/weidai11/cryptopp/issues/861/comments | 1 | 2019-07-06T07:04:10Z | 2019-07-06T07:12:29Z | https://github.com/weidai11/cryptopp/issues/861 | 464,826,067 | 861 |
[
"weidai11",
"cryptopp"
] | This issue has been nagging us for about 4 years, since we started testing with Asan. Also see [Issue 304](https://github.com/weidai11/cryptopp/issues/304).
Originally we thought (hoped?) it may be a false positive since the finding pointed to an address in our stack frame. We also were not able to duplicate with Va... | Asan finding in VMAC on i686 in inline asm | https://api.github.com/repos/weidai11/cryptopp/issues/860/comments | 2 | 2019-07-05T07:17:59Z | 2020-12-20T01:03:38Z | https://github.com/weidai11/cryptopp/issues/860 | 464,498,617 | 860 |
[
"weidai11",
"cryptopp"
] | The Gentoo folks caught a bug report at Issue 689162, [dev-libs/crypto++-8.2.0 with CXXFLAGS="-march=bdver1" - error: ‘_mm_roti_epi64’ was not declared in this scope](https://bugs.gentoo.org/689162):
```
x86_64-pc-linux-gnu-g++ -O2 -march=bdver1 -pipe -fPIC -pthread -pipe -msse4.1 -c blake2b_simd.cpp
blake2b_simd.... | AMD and error: use of undeclared identifier '_mm_roti_epi64' | https://api.github.com/repos/weidai11/cryptopp/issues/859/comments | 1 | 2019-07-02T20:40:52Z | 2020-12-20T01:03:48Z | https://github.com/weidai11/cryptopp/issues/859 | 463,425,829 | 859 |
[
"weidai11",
"cryptopp"
] | As discussed on the mailing list at [ECIES with no HMAC](https://groups.google.com/forum/#!topic/cryptopp-users/csUq-DqdWa8). After Crypto++ 5.6.5 was released we changed ECIES to align with Botan and Bouncy Castle. The change was mostly without incident, except...
It looks like `GetSymmetricKeyLength` took an unint... | ECIES and GetSymmetricKeyLength no longer uses MAC::DEFAULT_KEYLENGTH | https://api.github.com/repos/weidai11/cryptopp/issues/856/comments | 0 | 2019-07-01T22:26:31Z | 2020-12-20T01:04:02Z | https://github.com/weidai11/cryptopp/issues/856 | 462,938,031 | 856 |
[
"weidai11",
"cryptopp"
] | There is an issue reported by static analysis in `pwdbased.h` where not checking the results of the hmac processing can lead to a divide by zero.
Here is the hmac portion:
HMAC<T> hmac(secret, secretLen);
SecByteBlock buffer(hmac.DigestSize());
If `hmac.DigestSize()` returns 0, then this subsequent ca... | Possible divide by zero | https://api.github.com/repos/weidai11/cryptopp/issues/855/comments | 6 | 2019-06-28T14:18:58Z | 2019-07-01T15:22:50Z | https://github.com/weidai11/cryptopp/issues/855 | 462,057,771 | 855 |
[
"weidai11",
"cryptopp"
] | ### Crypto++ Issue Report
I am trying to build static lib .a for iPhone app
os macosx Mojave
Xcode 10.21
building master branch (currently 8.2)
Procedure building in console (building in Xcode fails with same problems):
1. Setting up environment
```
./setenv-ios.sh
Configuring for iPhoneOS (armv7)
XCODE_S... | Assembler errors when building with clang on MacOSX Mojave : error: unknown token in expression INTEL_NOPREFIX | https://api.github.com/repos/weidai11/cryptopp/issues/854/comments | 5 | 2019-06-27T18:57:10Z | 2019-06-30T12:25:48Z | https://github.com/weidai11/cryptopp/issues/854 | 461,697,115 | 854 |
[
"weidai11",
"cryptopp"
] | Hello,
I experiment using cryptopp on redhat 7.2 and got a mysterious problem.
Using valgring memcheck, I got:
```
==7472== Conditional jump or move depends on uninitialised value(s)
==7472== at 0x80DC3B2: BERGeneralDecoder::TransferTo2(BufferedTransformation&, unsigned long long&, std::string const&, bool)... | Issue on creating CryptoPP::BERGeneralDecoder object | https://api.github.com/repos/weidai11/cryptopp/issues/852/comments | 5 | 2019-06-07T15:24:47Z | 2019-06-11T16:01:23Z | https://github.com/weidai11/cryptopp/issues/852 | 453,569,931 | 852 |
[
"weidai11",
"cryptopp"
] | Clang, GCC and code review services like [lgtm](https://lgtm.com) have been nagging that the ASN.1 encoders and decoders have signatures that could match a copy constructor due to the default parameter of `asnTag`. Clang and GCC would do it on occasion at elevated warnings; while [lgtm](https://lgtm.com) does it during... | Refine ASN.1 encoders and decoders so they don't accidentally match copy ctor | https://api.github.com/repos/weidai11/cryptopp/issues/851/comments | 0 | 2019-06-04T06:43:38Z | 2019-06-04T06:54:03Z | https://github.com/weidai11/cryptopp/issues/851 | 451,823,832 | 851 |
[
"weidai11",
"cryptopp"
] | We cut-in BMI2 code paths for the `Integer` class at [Commit fb0bef1eb6e5](https://github.com/weidai11/cryptopp/commit/fb0bef1eb6e5) and [Commit 4952fa489d43](https://github.com/weidai11/cryptopp/commit/4952fa489d43). The changes made use of BMI2's `mulx` and `adcx` instructions. The instructions allow compilers greate... | Disable BMI2 code paths in Integer class | https://api.github.com/repos/weidai11/cryptopp/issues/850/comments | 1 | 2019-06-01T04:00:28Z | 2019-06-01T04:18:10Z | https://github.com/weidai11/cryptopp/issues/850 | 451,041,096 | 850 |
[
"weidai11",
"cryptopp"
] | Hello there,
I am using Debian 9.8 (Stretch). I am using Crypto++ version 8.2.0. downloaded from the Crypto++ website. I built the library using Make and the instructions on the [Wiki page](https://www.cryptopp.com/wiki/Linux#Build_and_Install_the_Library). I built my one-file program using:
g++ myfile.cpp -o... | Program stuck on MUL_16 (line 1411 in integer.cpp) | https://api.github.com/repos/weidai11/cryptopp/issues/849/comments | 3 | 2019-05-28T14:10:45Z | 2019-05-29T21:52:27Z | https://github.com/weidai11/cryptopp/issues/849 | 449,292,867 | 849 |
[
"weidai11",
"cryptopp"
] | ### Crypto++ Issue Report
Heap corruption when using x86_64-w64-mingw32-g++ 8.3.0
```
warning: HEAP[main.exe]:
warning: Invalid address specified to RtlFreeHeap( 0000000003590000, 00000000034488B0 )
Thread 1 received signal SIGTRAP, Trace/breakpoint trap.
0x00007ff9d6fc8c07 in ntdll!RtlpNtMakeTemporaryKey (... | Heap Corruption on Mingw64 | https://api.github.com/repos/weidai11/cryptopp/issues/848/comments | 3 | 2019-05-28T13:13:27Z | 2019-05-29T11:09:30Z | https://github.com/weidai11/cryptopp/issues/848 | 449,262,165 | 848 |
[
"weidai11",
"cryptopp"
] | Currently the Cryptogams SHA implementation comingles NEON and ARMv7 code. The caller calls `sha1_block_data_order`, and either ARMv7 or NEON executes depending on `CRYTPOGAMS_armcap` feature bits. The Cryptogams code does this internally. We can't check for NEON and call it independently.
Breaking out `sha1_block_d... | Add Cryptogams sha_xxx_neon functions | https://api.github.com/repos/weidai11/cryptopp/issues/847/comments | 0 | 2019-05-27T01:36:25Z | 2020-12-20T01:05:58Z | https://github.com/weidai11/cryptopp/issues/847 | 448,631,354 | 847 |
[
"weidai11",
"cryptopp"
] | After cutting in Cryptogams SHA for ARM (GH #837, GH #839, GH #841), loading the shared object results in:
LD_LIBRARY_PATH=./ ./cryptest.exe v
/home/test/cryptopp/.libs/lt-cryptest: error while loading shared
libraries: /home/test/cryptopp/.libs/libcryptopp.so.8: unexpected reloc type 0x03
The stati... | ARM and "unexpected reloc type 0x03" loading shared object | https://api.github.com/repos/weidai11/cryptopp/issues/846/comments | 0 | 2019-05-22T22:54:36Z | 2019-05-23T10:09:08Z | https://github.com/weidai11/cryptopp/issues/846 | 447,377,006 | 846 |
[
"weidai11",
"cryptopp"
] | The library uses two defines for Clang: `CRYPTOPP_APPLE_CLANG_VERSION` and `CRYPTOPP_LLVM_CLANG_VERSION`. The distinction is necessary because Apple does not pickup all LLVM patches, and Apple uses a different numbering scheme. Also see [Xcode Clang Version Record](https://gist.github.com/yamaya/2924292) GitHub.
Due... | Fix use of CRYPTOPP_CLANG_VERSION | https://api.github.com/repos/weidai11/cryptopp/issues/845/comments | 0 | 2019-05-21T07:14:35Z | 2020-12-20T01:06:28Z | https://github.com/weidai11/cryptopp/issues/845 | 446,453,521 | 845 |
[
"weidai11",
"cryptopp"
] | Since cutting over to Cryptogams SHA on 32-bit ARM, the numbers for Clang have not improved. For example, on a Tinkerboard @1.8 GHz:
***GCC***:
Hash|Provider|MB/s|Cpb
-- | -- | -- | --
MD5 | C++ | 245 | 7.00
SHA-1 | NEON | 223 | 7.69
SHA-256 | NEON | 88 | 19.50
***Clang***:
Hash|Provider|MB/s|Cpb
-- | ... | Performance is off for some algorithms on ARM with Clang | https://api.github.com/repos/weidai11/cryptopp/issues/844/comments | 1 | 2019-05-20T22:35:10Z | 2019-05-21T03:40:08Z | https://github.com/weidai11/cryptopp/issues/844 | 446,339,486 | 844 |
[
"weidai11",
"cryptopp"
] | Tested on latest git master on Linux 64 bit.
In my opinion, it should throw, not crash.
```cpp
#include <scrypt.h>
int main(void)
{
unsigned char out[32] = { 0 };
const unsigned char password[8] = { 0 };
const unsigned char salt[8] = { 0 };
::CryptoPP::Scrypt scrypt;
scrypt.DeriveK... | Scrypt with blocksize = 0 segfaults | https://api.github.com/repos/weidai11/cryptopp/issues/842/comments | 1 | 2019-05-19T12:28:13Z | 2020-12-20T01:06:42Z | https://github.com/weidai11/cryptopp/issues/842 | 445,814,225 | 842 |
[
"weidai11",
"cryptopp"
] | Add ARM SHA512 asm implementation from Cryptogams.
Cryptogams is Andy Polyakov's project used to create high speed crypto algorithms and share them with other developers. Cryptogams has a dual license. First is the OpenSSL license because Andy contributes to OpenSSL. Second is a BSD license for those who want a mor... | Add ARM SHA512 asm implementation from Cryptogams | https://api.github.com/repos/weidai11/cryptopp/issues/841/comments | 0 | 2019-05-19T12:09:13Z | 2020-12-20T01:06:57Z | https://github.com/weidai11/cryptopp/issues/841 | 445,812,359 | 841 |
[
"weidai11",
"cryptopp"
] | Add ARM SHA256 asm implementation from Cryptogams.
Cryptogams is Andy Polyakov's project used to create high speed crypto algorithms and share them with other developers. Cryptogams has a dual license. First is the OpenSSL license because Andy contributes to OpenSSL. Second is a BSD license for those who want a mor... | Add ARM SHA256 asm implementation from Cryptogams | https://api.github.com/repos/weidai11/cryptopp/issues/839/comments | 0 | 2019-05-19T09:27:36Z | 2020-12-20T01:07:07Z | https://github.com/weidai11/cryptopp/issues/839 | 445,798,575 | 839 |
[
"weidai11",
"cryptopp"
] | Add ARM SHA1 asm implementation from Cryptogams.
Cryptogams is Andy Polyakov's project used to create high speed crypto algorithms and share them with other developers. Cryptogams has a dual license. First is the OpenSSL license because Andy contributes to OpenSSL. Second is a BSD license for those who want a more ... | Add ARM SHA1 asm implementation from Cryptogams | https://api.github.com/repos/weidai11/cryptopp/issues/837/comments | 0 | 2019-05-18T10:39:16Z | 2020-12-20T01:07:31Z | https://github.com/weidai11/cryptopp/issues/837 | 445,703,364 | 837 |
[
"weidai11",
"cryptopp"
] | Currently we don't integrate well with Autoconf's feature tests. Autoconf would like to write a new `config.h` based on platform feature tests, but our `config.h` has stuff in it that Autoconf cannot handle. For example, our `config.h` header has:
```
#if defined(_MSC_VER) || defined(__BORLANDC__)
typedef signed ... | Make config.h more autoconf friendly | https://api.github.com/repos/weidai11/cryptopp/issues/835/comments | 1 | 2019-05-16T07:00:59Z | 2020-12-20T01:07:22Z | https://github.com/weidai11/cryptopp/issues/835 | 444,786,249 | 835 |
[
"weidai11",
"cryptopp"
] | libcrypto++ 8.1, gcc 4.9.4 running on linux x64.
The exactly same code works fine with gcc 4.5 on the same linux x64 environment, but after I upgraded GCC to 4.9, the same code triggered a SIGILL.
However, on the MSW/x64 platform, the same code compiled with GCC (MinGW) 4.9.2 can be executed correctly.
So, fo... | GCC 4.9 linux x64 target crash with SIGILL | https://api.github.com/repos/weidai11/cryptopp/issues/834/comments | 15 | 2019-05-16T04:45:01Z | 2019-05-18T02:34:11Z | https://github.com/weidai11/cryptopp/issues/834 | 444,751,967 | 834 |
[
"weidai11",
"cryptopp"
] | I've build a [cryptography implementation differential fuzzer](https://github.com/guidovranken/cryptofuzz) that has been running on OSS-Fuzz for a few weeks and has found some [nice bugs](https://github.com/guidovranken/cryptofuzz#hall-of-fame).
I will be integrating Crypto++ support for my fuzzer into OSS-Fuzz shor... | OSS-Fuzz integration | https://api.github.com/repos/weidai11/cryptopp/issues/833/comments | 5 | 2019-05-06T11:53:32Z | 2019-05-18T08:45:13Z | https://github.com/weidai11/cryptopp/issues/833 | 440,662,414 | 833 |
[
"weidai11",
"cryptopp"
] | I built a statis lib but it could't work, I got an incorrent result(using CRC32, MD5 or SHA1), but I run the cryptest.exe well, it showed all test passed.
And this problem doesn't exists in my server machine.
my local machine runs windows 10 2019 LTSC(64Bit), and my server machine runs windows 10 2016 LTSB((64Bit)), ... | static lib can't work good | https://api.github.com/repos/weidai11/cryptopp/issues/832/comments | 1 | 2019-05-02T13:48:19Z | 2019-05-02T15:56:32Z | https://github.com/weidai11/cryptopp/issues/832 | 439,600,947 | 832 |
[
"weidai11",
"cryptopp"
] | Native testing on a [Tritium H3 dev-board](https://libre.computer/products/boards/all-h3-cc/) with Cortex-A7 running Armbian, which is a Ubuntu Bionic derivative:
$ clang -dumpmachine
armv8l-unknown-linux-gnueabihf
And GCC on the same machine:
$ gcc -dumpmachine
arm-linux-gnueabihf
We dete... | Gracefully handle Clang triplet armv8l-unknown-linux-gnueabihf | https://api.github.com/repos/weidai11/cryptopp/issues/831/comments | 1 | 2019-05-01T05:27:30Z | 2020-12-20T01:07:48Z | https://github.com/weidai11/cryptopp/issues/831 | 439,072,701 | 831 |
[
"weidai11",
"cryptopp"
] | `xed25519.cpp` is generating about three findings during self test with UBsan. The findings occur on a Tritium H3 ARM A-32 dev-board. Below is a sample finding.
```
xed25519.cpp:856:97: runtime error: reference binding to misaligned address 0xbe8cfaa4 for type 'const struct ed25519PrivateKey', which requires 8 byte... | xed25519.cpp:856:97: runtime error: reference binding to misaligned address | https://api.github.com/repos/weidai11/cryptopp/issues/829/comments | 1 | 2019-05-01T00:28:22Z | 2020-12-20T01:08:11Z | https://github.com/weidai11/cryptopp/issues/829 | 439,031,299 | 829 |
[
"weidai11",
"cryptopp"
] | We cut-over to inline functions that retrieve a `BytePtr` or `ConstBytePtr` from a `std::string`. The function handles the casts and asserts so we don't have to use the pattern throughout the code.
We are catching some asserts in Debug builds that we could sidestep. The current code in `datatest.cpp` uses a `BytePtr... | Debug asserts in TestDataNameValuePairs | https://api.github.com/repos/weidai11/cryptopp/issues/827/comments | 1 | 2019-04-29T04:02:30Z | 2019-04-29T04:16:45Z | https://github.com/weidai11/cryptopp/issues/827 | 438,142,351 | 827 |
[
"weidai11",
"cryptopp"
] | Use PowerPC unaligned loads and stores with Power8.
We are seeing some trouble using Power7. | Use PowerPC unaligned loads and stores with Power8 | https://api.github.com/repos/weidai11/cryptopp/issues/825/comments | 1 | 2019-04-28T00:21:55Z | 2019-04-28T01:18:00Z | https://github.com/weidai11/cryptopp/issues/825 | 437,996,877 | 825 |
[
"weidai11",
"cryptopp"
] | ```
std::string result_str;
CryptoPP::CBC_Mode<CryptoPP::SKIPJACK>::Encryption e;
CryptoPP::byte key[10] = { 0x00, 0x99, 0x88, 0x77, 0x66, 0x55, 0x44, 0x33, 0x22, 0x11 };
CryptoPP::byte plain[8] = { 0x33, 0x22, 0x11, 0x00, 0xdd, 0xcc, 0xbb, 0xaa };
d.SetKey(key, sizeof(key));
std::string i... | SKIPJACK encryption gives wrong result | https://api.github.com/repos/weidai11/cryptopp/issues/824/comments | 5 | 2019-04-26T15:12:57Z | 2019-04-28T03:33:45Z | https://github.com/weidai11/cryptopp/issues/824 | 437,720,577 | 824 |
[
"weidai11",
"cryptopp"
] | ### Crypto++ Issue Report
Thanks for taking the time to report an issue. Reporting issues helps us improve stability and reliability for all users, so it is a valuable contribution.
Please do not ask questions in the bug tracker. Please ask questions on the Crypto++ Users List at http://groups.google.com/forum/#!... | CRC32 value is | https://api.github.com/repos/weidai11/cryptopp/issues/823/comments | 0 | 2019-04-20T10:32:14Z | 2019-04-20T16:15:04Z | https://github.com/weidai11/cryptopp/issues/823 | 435,382,845 | 823 |
[
"weidai11",
"cryptopp"
] | I am trying to cross compile from my Ubuntu 14.04 i686 32bit (LXC) for a Qnap NAS (GCC 4.3.6 i686 32bit)... to include it for UrBackup
I am stuck on this error
```
i686-QNAP-linux-gnu-g++ -O2 -fPIC -I/opt/QUrBackup/include -msse2 -c donna_sse.cpp
i686-QNAP-linux-gnu-g++ -O2 -fPIC -I/opt/QUrBackup/include -c d... | cross compile for i686 (Qnap NAS failed) | https://api.github.com/repos/weidai11/cryptopp/issues/822/comments | 4 | 2019-04-07T10:07:58Z | 2020-12-20T01:09:16Z | https://github.com/weidai11/cryptopp/issues/822 | 430,126,852 | 822 |
[
"weidai11",
"cryptopp"
] | Including `"hmac.h"` yields the following compiler warning when compiling with cl.exe (2017 version):
```
...\cryptopp\seckey.h(172): warning C4296: '>=': expression is always true
...\cryptopp\hmac.h(17): note: see reference to class template instantiation 'CryptoPP::VariableKeyLength<16,0,2147483647,1,4,0>' be... | Compiler warning in hmac.h | https://api.github.com/repos/weidai11/cryptopp/issues/821/comments | 1 | 2019-03-25T18:35:11Z | 2019-04-28T01:38:45Z | https://github.com/weidai11/cryptopp/issues/821 | 425,055,552 | 821 |
[
"weidai11",
"cryptopp"
] | crypto++ 8.1: shake.h
The Google Native Client compiler complain something like: "SHACK128: there is no field named SHAKE_Final", we must use the **full template name** to fix it:
```C++
// ...
SHAKE128(unsigned int outputSize) : SHAKE_Final<128>(outputSize) {} // NaCl compiler fix
// ...
SHAKE256(unsigned int ... | shake.h not compatible for the NaCl GCC compiler | https://api.github.com/repos/weidai11/cryptopp/issues/820/comments | 1 | 2019-03-23T18:46:57Z | 2020-12-20T01:10:06Z | https://github.com/weidai11/cryptopp/issues/820 | 424,532,416 | 820 |
[
"weidai11",
"cryptopp"
] | ### Crypto++ Issue Report
Thanks for taking the time to report an issue. Reporting issues helps us improve stability and reliability for all users, so it is a valuable contribution.
Please do not ask questions in the bug tracker. Please ask questions on the Crypto++ Users List at http://groups.google.com/forum/#!... | VS2013 compile error | https://api.github.com/repos/weidai11/cryptopp/issues/819/comments | 2 | 2019-03-21T02:40:50Z | 2023-08-17T15:49:23Z | https://github.com/weidai11/cryptopp/issues/819 | 423,551,494 | 819 |
[
"weidai11",
"cryptopp"
] | GCC version: gcc version 4.4.6 20110731 (Red Hat 4.4.6-4) (GCC)
run make command and compile fail, below is the last message:
```
g++ -DNDEBUG -g2 -O3 -DCRYPTOPP_DISABLE_AVX2 -fPIC -pthread -pipe -c seed.cpp
g++ -DNDEBUG -g2 -O3 -DCRYPTOPP_DISABLE_AVX2 -fPIC -pthread -pipe -c serpent.cpp
g++ -DNDEBUG -g2 -O3 -DC... | compile error when building version 810 | https://api.github.com/repos/weidai11/cryptopp/issues/818/comments | 2 | 2019-03-18T11:15:50Z | 2019-03-18T12:08:27Z | https://github.com/weidai11/cryptopp/issues/818 | 422,163,085 | 818 |
[
"weidai11",
"cryptopp"
] | I found a strange behaviour using a `FileSource` to decrypt a text encrypted with AES/EAX using both channels provided by `AuthenticatedEncryptionFilter` and `AuthenticatedDecryptionFilter`: it seems that the operations sequence used (successfully) with a `StringSource` cannot be used with a `FileSource` instead.
Digg... | AuthenticatedDecryptionFilter with AAD throws an exception when used with a FileSource | https://api.github.com/repos/weidai11/cryptopp/issues/817/comments | 6 | 2019-03-06T16:28:45Z | 2020-12-20T01:10:25Z | https://github.com/weidai11/cryptopp/issues/817 | 417,895,688 | 817 |
[
"weidai11",
"cryptopp"
] | This has been mentioned in the wiki as a possible solution. Since I've upgraded my code to C++17 and `std::byte`, I have to `reinterpret_cast` my buffers to `CryptoPP::byte`. I think this is a usability issue.
Can you add overloads that take `std::byte*` to functions that take `CryptoPP::byte*`? | Add std::byte overloads | https://api.github.com/repos/weidai11/cryptopp/issues/816/comments | 5 | 2019-03-06T16:21:09Z | 2019-03-09T16:45:06Z | https://github.com/weidai11/cryptopp/issues/816 | 417,891,752 | 816 |
[
"weidai11",
"cryptopp"
] | This is a side/tangential issue from [Issue 812](https://github.com/weidai11/cryptopp/issues/812#issuecomment-468215577). Here is the relevant information from the 812 issue:
-----
You actually tickled a bug in our Makefile. I've known about it for several years, but I never addressed it. The problem is, we don't... | GNUmakefile needs to use separate variable for CXXFLAGS | https://api.github.com/repos/weidai11/cryptopp/issues/814/comments | 2 | 2019-02-28T10:32:59Z | 2020-12-20T01:10:39Z | https://github.com/weidai11/cryptopp/issues/814 | 415,553,544 | 814 |
[
"weidai11",
"cryptopp"
] | The makefile tries to pre-qualify NEON (for lack of a better term), and sets `IS_NEON` accordingly. If `IS_NEON=1`, then we go on to perform test compiles to see if `-mfloat-abi=X -mfpu=neon` (and friends) actually work. Effectively we are performing a test to see if we should perform another test.
The `IS_NEON` fla... | Remove IS_NEON from Makefile | https://api.github.com/repos/weidai11/cryptopp/issues/813/comments | 1 | 2019-02-28T00:34:46Z | 2020-12-20T01:10:51Z | https://github.com/weidai11/cryptopp/issues/813 | 415,391,575 | 813 |
[
"weidai11",
"cryptopp"
] | Using Fedora 30, I cannot update to cryptopp 8.0.0/8.1.0
Seems like CPU features are miss-detected as I cannot see any ASM_FLAGS been used in "some" cases.
Build attempt for f31,f29, f28
https://koji.fedoraproject.org/koji/taskinfo?taskID=33066081
https://koji.fedoraproject.org/koji/taskinfo?taskID=33066857
http... | Build fails on fedora30+ (CPU features miss-detected) | https://api.github.com/repos/weidai11/cryptopp/issues/812/comments | 11 | 2019-02-26T17:12:18Z | 2019-02-28T11:45:02Z | https://github.com/weidai11/cryptopp/issues/812 | 414,723,029 | 812 |
[
"weidai11",
"cryptopp"
] | ### Crypto++ 8.0 Issue Report
GCC 4.7 (gcc-linaro-arm-linux-gnueabihf-4.7) with ARMv8 and NEON enabled:
```
-march=armv7-a
-mfpu=neon-vfpv4
```
We encrypt the plaintext with Speck128-128 and dcrypt it immediately on a Freescale i.MX6 UltraLite processor, and the result is wrong.
If we disabled the NEON op... | The ARM NEON Speck optimization is wrong | https://api.github.com/repos/weidai11/cryptopp/issues/808/comments | 30 | 2019-02-14T22:09:58Z | 2019-02-15T18:59:16Z | https://github.com/weidai11/cryptopp/issues/808 | 410,515,188 | 808 |
[
"weidai11",
"cryptopp"
] | ### Crypto++ 8.0 Issue Report
We have some disk data encrypted by Crypto++ 7.0 with ChaCha8, We use the same 8 rounds ChaCha algorithm provided by 8.0 to decrypt it with exactly same key and iv, but the result is wrong.
We have try a few other algorithms, both encrypted using 7.0, then decrypt them use the 8.0, t... | ChaCha Algorithm changed? | https://api.github.com/repos/weidai11/cryptopp/issues/807/comments | 15 | 2019-02-13T21:41:11Z | 2019-02-23T05:23:40Z | https://github.com/weidai11/cryptopp/issues/807 | 410,016,057 | 807 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.