issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 261k ⌀ | issue_title stringlengths 1 925 | issue_comments_url stringlengths 56 81 | issue_comments_count int64 0 2.5k | issue_created_at stringlengths 20 20 | issue_updated_at stringlengths 20 20 | issue_html_url stringlengths 37 62 | issue_github_id int64 387k 2.46B | issue_number int64 1 127k |
|---|---|---|---|---|---|---|---|---|---|
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | How to extract audio from video file without knowing the audio track ID? | https://api.github.com/repos/gpac/gpac/issues/2187/comments | 2 | 2022-05-06T12:06:46Z | 2022-05-06T16:26:55Z | https://github.com/gpac/gpac/issues/2187 | 1,227,780,953 | 2,187 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | Can I use MP4Box to split one video into multiple parts and merge them into one video? | https://api.github.com/repos/gpac/gpac/issues/2186/comments | 6 | 2022-05-04T18:23:16Z | 2022-05-18T09:09:27Z | https://github.com/gpac/gpac/issues/2186 | 1,225,724,202 | 2,186 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | Can I use mp4box to set audio ID# when concat multiple video files? | https://api.github.com/repos/gpac/gpac/issues/2185/comments | 1 | 2022-05-04T11:07:15Z | 2022-05-17T10:00:09Z | https://github.com/gpac/gpac/issues/2185 | 1,225,223,268 | 2,185 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | Can I use MP4Box to combine audio and video with some delay into one video file? | https://api.github.com/repos/gpac/gpac/issues/2184/comments | 4 | 2022-05-03T20:00:56Z | 2022-05-06T15:51:23Z | https://github.com/gpac/gpac/issues/2184 | 1,224,564,603 | 2,184 |
[
"gpac",
"gpac"
] | Hello!
I've noticed that MP4Box is changing the values of my HDR10 mastering display characteristics (i.e. the SMTPTE ST.2086 metadata that x265 injects into the HEVC bitstream).
When I use mediainfo to inspect the original MP4 out of ffmpeg I see what I specified:
```
Mastering display color primaries :... | MP4Box changing HDR10 SMPTE ST.2086 (mastering display characteristics) metadata? | https://api.github.com/repos/gpac/gpac/issues/2183/comments | 1 | 2022-05-03T19:15:07Z | 2022-05-17T12:43:46Z | https://github.com/gpac/gpac/issues/2183 | 1,224,510,290 | 2,183 |
[
"gpac",
"gpac"
] | poc.py is available [here](https://drive.google.com/file/d/1M-H0WLIomHlEfyr2rJlfZsV2INDlKgqO/view?usp=sharing)
```
Description
A malicious RTSP server can trigger a stack buffer overflow via an RTSP packet with an excessively long content-length due to no bounds check when copying into a fixed sized buffer.
Pro... | Stack buffer overflow in RTSP packet parsing | https://api.github.com/repos/gpac/gpac/issues/2182/comments | 0 | 2022-05-02T16:48:54Z | 2022-05-16T10:30:00Z | https://github.com/gpac/gpac/issues/2182 | 1,223,107,663 | 2,182 |
[
"gpac",
"gpac"
] | Command used:
`MP4Box -add BL_RPU.hevc:dv-profile=5 -add "1.eng.eac3":timescale=1000:delay=3003:sopt:gfreg=ffdmx -lang 2=eng -brand mp42isom -ab dby1 output.mp4`
I checked the output using ffprobe to check the resulting file with this command:
`ffprobe -loglevel error -show_entries stream=start_time:stream=time_... | delay not used when using timescale | https://api.github.com/repos/gpac/gpac/issues/2181/comments | 1 | 2022-04-28T21:34:55Z | 2022-05-17T10:13:25Z | https://github.com/gpac/gpac/issues/2181 | 1,219,324,781 | 2,181 |
[
"gpac",
"gpac"
] | Hello there, I'm using a GPAC version compiled with ffmpeg and libkvazaar to try and generate the MPD and segmets from a live feed.
when i hit this
gpac -i ./1.mp4 ffsws:FID=S -+kvazaar-params=tiles=3x3,slices=tiles,mv-constraint=frametilemargin,rc-algorithm=lambda enc:SID=S:c=libkvazaar:b=1m:fintra=1:rc @ tile... | i want to ask RTMP to hevc tile some question | https://api.github.com/repos/gpac/gpac/issues/2180/comments | 4 | 2022-04-28T05:03:06Z | 2022-05-07T11:26:51Z | https://github.com/gpac/gpac/issues/2180 | 1,218,201,286 | 2,180 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | [BUG] heap buffer overflow in gf_utf8_wcslen, utils/utf.c:442 | https://api.github.com/repos/gpac/gpac/issues/2179/comments | 4 | 2022-04-25T14:26:20Z | 2023-03-07T12:37:47Z | https://github.com/gpac/gpac/issues/2179 | 1,214,594,854 | 2,179 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | MP4Box input file from server | https://api.github.com/repos/gpac/gpac/issues/2178/comments | 14 | 2022-04-20T10:35:40Z | 2022-04-20T14:50:49Z | https://github.com/gpac/gpac/issues/2178 | 1,209,497,928 | 2,178 |
[
"gpac",
"gpac"
] |
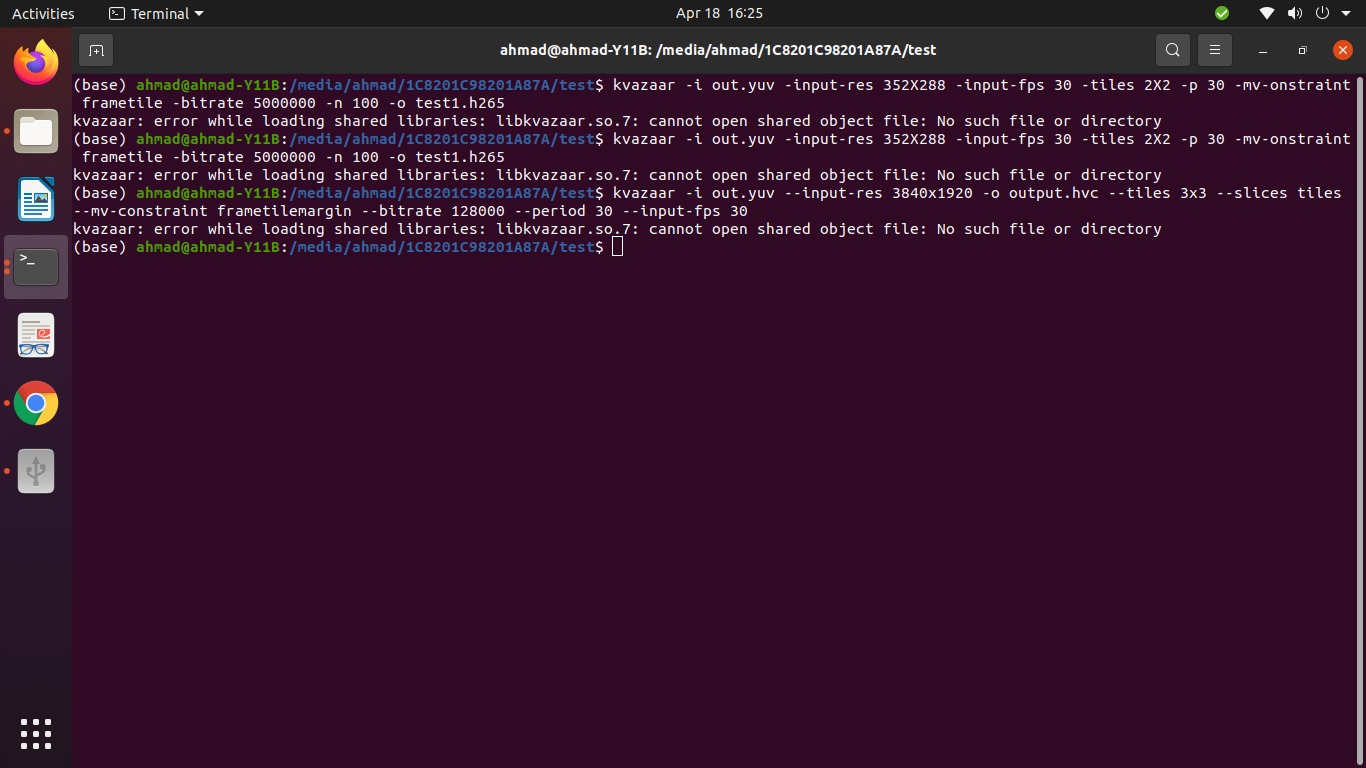
We have installed kvazaar on our Linux system for the tiling of 360-degree videos. After compiling and installing when we are trying to run any command, we are getting th... | libkvazaar.so.7 error | https://api.github.com/repos/gpac/gpac/issues/2177/comments | 1 | 2022-04-18T14:44:01Z | 2022-04-18T15:06:27Z | https://github.com/gpac/gpac/issues/2177 | 1,207,119,804 | 2,177 |
[
"gpac",
"gpac"
] | [INSTALLED: windows latest mid-april 2022 GPAC dev versions]
OBJECTIVE: To find out the meaning of output message ~>> "[isom/avcc] Missing REXT profile signaling, patching."
I RUN:
mp4box -udta 1:type=name:str=homevid001 -udta 2:type=name:str=homeaud001 home001.mp4
In-place editing works brilliantly... | "mp4box -udta ..." naming track IDs works YET outputs ~>[isom/avcc] Missing REXT profile signaling, patching. | https://api.github.com/repos/gpac/gpac/issues/2176/comments | 2 | 2022-04-17T09:39:53Z | 2022-04-19T11:10:50Z | https://github.com/gpac/gpac/issues/2176 | 1,206,329,469 | 2,176 |
[
"gpac",
"gpac"
] | # Description
When GPAC tries to parse a MP4 file, it calls the function `diST_box_read()` to read from video. In this funtion, it allocates a buffer `str` with fixed length. However, content read from `bs` is controllable by user, so is the length, which causes a buffer overflow.
```
char str[1024];
i=0;
... | GPAC-2.0.0 MP4Box: stack overflow with unlimited length and controllable content in diST_box_read | https://api.github.com/repos/gpac/gpac/issues/2175/comments | 1 | 2022-04-16T08:21:46Z | 2022-04-22T18:29:03Z | https://github.com/gpac/gpac/issues/2175 | 1,206,053,267 | 2,175 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | [BUG] heap buffer overflow in gp_rtp_builder_do_hevc | https://api.github.com/repos/gpac/gpac/issues/2173/comments | 0 | 2022-04-16T08:01:38Z | 2022-08-03T09:45:02Z | https://github.com/gpac/gpac/issues/2173 | 1,206,048,984 | 2,173 |
[
"gpac",
"gpac"
] | I'm using MP4Box to tag some AAC audio files (using the **-itags option**) and I'm having difficulty getting the Genre metadata to display in the players that I've tested the files in.
The other metadata fields are showing up across all players, but Genre does not show in iTunes, Windows Media Player, VLC, or Audaci... | MP4Box genre metadata tags not displaying across different players | https://api.github.com/repos/gpac/gpac/issues/2172/comments | 1 | 2022-04-14T22:00:28Z | 2022-04-19T12:29:36Z | https://github.com/gpac/gpac/issues/2172 | 1,205,049,562 | 2,172 |
[
"gpac",
"gpac"
] | It seems like example in [dash-low-latency-live-encoding](https://github.com/gpac/gpac/wiki/dash_low_latency#dash-low-latency-live-encoding) cannot work correctly when simply change input to RTMP. The command I use is:
```
gpac \
-i rtmp://127.0.0.1:1935/live/test:gpac:rtmp_listen=1:FID=1 \
ffsws:os... | RTMP input cannot encode in multi-qualitis by using given example | https://api.github.com/repos/gpac/gpac/issues/2171/comments | 6 | 2022-04-14T15:33:57Z | 2022-04-15T16:00:18Z | https://github.com/gpac/gpac/issues/2171 | 1,204,684,755 | 2,171 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough infor... | Adding a second subtitle track generate error messages | https://api.github.com/repos/gpac/gpac/issues/2170/comments | 5 | 2022-04-12T13:32:07Z | 2022-05-17T06:36:53Z | https://github.com/gpac/gpac/issues/2170 | 1,201,858,545 | 2,170 |
[
"gpac",
"gpac"
] | Raised in #2167 where the Python part of the doc was empty after the code was moved. Could we check that? Thx | Check doxygen_warnings.txt is empty when generating doc | https://api.github.com/repos/gpac/gpac/issues/2169/comments | 1 | 2022-04-10T15:46:48Z | 2022-04-12T13:05:29Z | https://github.com/gpac/gpac/issues/2169 | 1,199,079,989 | 2,169 |
[
"gpac",
"gpac"
] | Hello,
I'm trying to play a video in VR mode using HEVC and DASH SRD as follows:
`gpac -i DoiSuthep_dash_22_50.mpd#VR @ compositor @ vout`
But after a few seconds the video seems to have colour conversion issues as shown below:

I want to make my own mpeg dash ABS
I want to know the user environment bandwidth and total use Bandwidth for playing HEVC TILE video | Python APIs where is it | https://api.github.com/repos/gpac/gpac/issues/2167/comments | 7 | 2022-04-09T13:00:17Z | 2022-04-12T08:59:07Z | https://github.com/gpac/gpac/issues/2167 | 1,198,586,726 | 2,167 |
[
"gpac",
"gpac"
] | **version info:**
```
root@d8a714203f6e:# ./MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev87-g053aae8-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your research:
GPAC Filters: https://doi.org/10.1145/3339825.3394929
GPAC: https://do... | AddressSanitizer: heap-buffer-overflow in gf_isom_add_sample_aux_info_internal, isomedia/isom_write.c:8515 | https://api.github.com/repos/gpac/gpac/issues/2166/comments | 3 | 2022-04-08T09:01:21Z | 2022-04-12T11:27:28Z | https://github.com/gpac/gpac/issues/2166 | 1,197,040,939 | 2,166 |
[
"gpac",
"gpac"
] | **version info:**
```
root@d8a714203f6e:# ./MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev87-g053aae8-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your research:
GPAC Filters: https://doi.org/10.1145/3339825.3394929
GPAC: https://do... | Assertion failed in BS_ReadByte, utils/bitstream.c:383 | https://api.github.com/repos/gpac/gpac/issues/2165/comments | 0 | 2022-04-08T08:28:19Z | 2022-04-12T09:01:22Z | https://github.com/gpac/gpac/issues/2165 | 1,197,007,820 | 2,165 |
[
"gpac",
"gpac"
] | poc.py is available [here](https://drive.google.com/file/d/1iH28RyOdIbMDdUONKZSBbJU0Y6QiAEl_/view?usp=sharing)
```
Description
A malicious server can trigger an out-of-bounds heap write via a specially crafted SDP packet due to no bounds check when parsing time zone information into the AdjustmentTime and Adjust... | Controlled heap buffer overflow in SDP packet parsing | https://api.github.com/repos/gpac/gpac/issues/2164/comments | 2 | 2022-04-04T08:02:09Z | 2022-04-12T08:40:25Z | https://github.com/gpac/gpac/issues/2164 | 1,191,405,764 | 2,164 |
[
"gpac",
"gpac"
] | **version info:**
```
root@d8a714203f6e:# ./MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev87-g053aae8-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your research:
GPAC Filters: https://doi.org/10.1145/3339825.3394929
GPAC: https://do... | NULL Pointer Dereference still exists in gf_isom_parse_movie_boxes_internal | https://api.github.com/repos/gpac/gpac/issues/2163/comments | 1 | 2022-04-01T12:17:54Z | 2022-04-12T09:01:21Z | https://github.com/gpac/gpac/issues/2163 | 1,189,714,047 | 2,163 |
[
"gpac",
"gpac"
] | poc.py is available [here](https://drive.google.com/file/d/1iH28RyOdIbMDdUONKZSBbJU0Y6QiAEl_/view?usp=sharing)
```
Description
A malicious server can trigger an out-of-bounds heap write via a specially crafted SDP packet due to no bounds check when parsing time zone information into the AdjustmentTime and Adjust... | Controlled heap buffer overflow in SDP packet parsing | https://api.github.com/repos/gpac/gpac/issues/2162/comments | 0 | 2022-04-01T07:35:21Z | 2022-04-11T16:32:35Z | https://github.com/gpac/gpac/issues/2162 | 1,189,381,531 | 2,162 |
[
"gpac",
"gpac"
] | Python support in GPAC 2.2 is incomplete: it needs the package installer (pip). So we can install the library ("pip install gpac"). Manual installation of Python modules is strongly discouraged by the Python Packaging Authority (PyPA). Thanks. | GPAC 2.2 - Python support incomplete - needs package installer (pip) | https://api.github.com/repos/gpac/gpac/issues/2161/comments | 1 | 2022-03-31T18:03:47Z | 2022-05-16T10:10:58Z | https://github.com/gpac/gpac/issues/2161 | 1,188,444,928 | 2,161 |
[
"gpac",
"gpac"
] | I am trying to do tiling using this command.
MP4Box -dash 1000 [other dash params] source.mp4:desc_as=<SupplementalProperty schemeIdUri=\"urn:mpeg:dash:srd:2014\" value=\"0,0,1,1,1,2,2\"/>
but this is showing a syntax error every time I implement this. Different other params were also tried but every time the sa... | Syntax not valid issue. | https://api.github.com/repos/gpac/gpac/issues/2160/comments | 4 | 2022-03-31T16:01:24Z | 2022-04-12T11:04:19Z | https://github.com/gpac/gpac/issues/2160 | 1,188,308,737 | 2,160 |
[
"gpac",
"gpac"
] | [POC](https://mega.nz/file/K9J1xIja#EKR-ls4tmAMFoXzHnWIxBA7fqzgFXcDgEUqFC2c5tUc)
```
Description
A inf loop security issue in gpac/gpac
Proof of Concept
The issue occurs in code: src/media_tools/avilib.c#L1974, when the gpac avidmx filter parses the AVI format file.
choose a simple AVI format file, the da... | Infinite loop | https://api.github.com/repos/gpac/gpac/issues/2159/comments | 0 | 2022-03-31T08:32:28Z | 2022-03-31T11:57:10Z | https://github.com/gpac/gpac/issues/2159 | 1,187,707,067 | 2,159 |
[
"gpac",
"gpac"
] | Hi,
Do you have in your roadmap add support to SCTE-35?
If not.... I can do it, but maybe I need help to know the project structure.
Thanks and awesome project!
| Add Support to SCTE - 35 | https://api.github.com/repos/gpac/gpac/issues/2158/comments | 11 | 2022-03-30T19:10:32Z | 2024-05-27T22:01:36Z | https://github.com/gpac/gpac/issues/2158 | 1,186,877,696 | 2,158 |
[
"gpac",
"gpac"
] | Hello, I successfully installed the osmo4 apk in oculus quest2, and i can open the osmo4. But there is no response when I click on icons. Any ideas about this? Thanks
| Osmo4 does not work in Oculus quest 2 | https://api.github.com/repos/gpac/gpac/issues/2157/comments | 1 | 2022-03-30T17:54:16Z | 2022-04-12T09:04:29Z | https://github.com/gpac/gpac/issues/2157 | 1,186,796,778 | 2,157 |
[
"gpac",
"gpac"
] | **Description**
A NULL pointer dereference vulnerability in `gf_isom_parse_movie_boxes_internal` function (`isomedia/isom_intern.c:392`) due to a missing check before using the pointer.
**Version**
```bash
MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev79-gdf29bc8a0-master
(c) 2000-2022 Telecom P... | NULL Pointer Dereference in gf_isom_parse_movie_boxes_internal | https://api.github.com/repos/gpac/gpac/issues/2155/comments | 0 | 2022-03-28T22:20:02Z | 2022-03-29T15:07:21Z | https://github.com/gpac/gpac/issues/2155 | 1,184,058,973 | 2,155 |
[
"gpac",
"gpac"
] |
poc-clean.svg available [here](https://drive.google.com/file/d/1Sw17h45RhIcfhEQKRj5A5MwPhYWNuo2p/view?usp=sharing)
```
Description
Attempting to parse a XML/SVG file containing an <!ENTITY with a sufficiently long name into a fixed sized, stack allocated buffer causes an overflow.
Proof of Concept
./bin/... | Stack buffer overflow in XML entity parsing | https://api.github.com/repos/gpac/gpac/issues/2154/comments | 0 | 2022-03-28T18:49:44Z | 2022-03-29T15:07:20Z | https://github.com/gpac/gpac/issues/2154 | 1,183,848,264 | 2,154 |
[
"gpac",
"gpac"
] | https://drive.google.com/file/d/1BQ49f00OCCs-eYouEcr_xOybrq7pkMol/view?usp=sharing
```
Proof of Concept
version
./bin/gcc/MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev65-g718843df4-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your research:
... | Null Pointer Dereference Caused Segmentation Fault | https://api.github.com/repos/gpac/gpac/issues/2153/comments | 0 | 2022-03-27T16:11:27Z | 2022-03-29T15:07:20Z | https://github.com/gpac/gpac/issues/2153 | 1,182,580,518 | 2,153 |
[
"gpac",
"gpac"
] | **Description**
I'm using GPAC to recreate DASH mpd's and HLS playlists. That's to simulate an event from a static asset, or creating a new playlist from 2 individual static assets.
```
gpac --forward=segb -i asset/manifest.mpd -i asset2/manifest.mpd -o merged.mpd:sigfrag:dual
```
```
gpac --forward=segb -i ass... | Missing directory in HLS playlist generated from existing MPD | https://api.github.com/repos/gpac/gpac/issues/2152/comments | 2 | 2022-03-24T09:41:09Z | 2022-04-06T07:34:52Z | https://github.com/gpac/gpac/issues/2152 | 1,179,253,803 | 2,152 |
[
"gpac",
"gpac"
] | I'm trying to use MP4Box to tag some AAC audio files (using the **-itags option**) and I'm getting an unexpected error when trying to add these two tags:
- record_company (A9mak)
- publisher (A9pub)
MP4Box reports an error for them as:
`[iso file] Unknown box type A9mak` respectively
`[iso file] Unknown box t... | Tagging of AAC files with MP4Box -itags fails for record_company (A9mak), publisher (A9pub) and a few other tags | https://api.github.com/repos/gpac/gpac/issues/2151/comments | 1 | 2022-03-23T01:00:50Z | 2022-03-30T09:00:32Z | https://github.com/gpac/gpac/issues/2151 | 1,177,463,487 | 2,151 |
[
"gpac",
"gpac"
] | I want to add/cat file with this command: `-add /mnt/sdcard/newtarget3.mp4 /mnt/sdcard/media.mp4` using mp4box android.
Then i get the following output: `[31mCannot open destination file /mnt/sdcard/media.mp4: I/O Error`
`[0m`
Thanks for reporting your issue. Please make sure these boxes are checked before subm... | MP4Box Android: I/O Error | https://api.github.com/repos/gpac/gpac/issues/2150/comments | 1 | 2022-03-22T04:58:43Z | 2022-05-18T16:32:15Z | https://github.com/gpac/gpac/issues/2150 | 1,176,267,335 | 2,150 |
[
"gpac",
"gpac"
] | [poc.zip](https://github.com/gpac/gpac/files/8311643/poc.zip)
```
Description
Null Pointer Dereference in gpac
Proof of Concept
Version:
~/fuzzing/gpac/gpac/bin/gcc/MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev15-g6c0f4ff03-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpa... | Untrusted Pointer Dereference | https://api.github.com/repos/gpac/gpac/issues/2149/comments | 0 | 2022-03-20T16:24:25Z | 2022-03-21T10:52:11Z | https://github.com/gpac/gpac/issues/2149 | 1,174,603,686 | 2,149 |
[
"gpac",
"gpac"
] | MP4Box.exe has an `pssh=m` option to write PSSH atom only in a manifest `<cenc:pssh>xxx</cenc:pssh>` element. Is it possible to omit PSSH from both init.mp4 and manifest, maybe `pssh=none` option?
Additionally is it possible to remove `PSSH` atom from the existing init.mp4 file? At the moment I am using a java appli... | Omit PSSH from init.mp4 and manifest.mpd? | https://api.github.com/repos/gpac/gpac/issues/2148/comments | 2 | 2022-03-17T08:28:54Z | 2022-03-22T15:27:21Z | https://github.com/gpac/gpac/issues/2148 | 1,172,074,711 | 2,148 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [ ] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ ] I give enough info... | Is there a player to playback a live.mpd session for Unreal Engine? | https://api.github.com/repos/gpac/gpac/issues/2147/comments | 2 | 2022-03-17T05:54:16Z | 2022-03-21T15:55:33Z | https://github.com/gpac/gpac/issues/2147 | 1,171,963,013 | 2,147 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Possible Bug - Segmentation fault found | https://api.github.com/repos/gpac/gpac/issues/2146/comments | 2 | 2022-03-17T00:24:19Z | 2022-07-31T22:03:05Z | https://github.com/gpac/gpac/issues/2146 | 1,171,725,165 | 2,146 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [ ] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | [BUG] several possible unfix bugs | https://api.github.com/repos/gpac/gpac/issues/2144/comments | 1 | 2022-03-16T20:48:25Z | 2022-03-21T15:00:59Z | https://github.com/gpac/gpac/issues/2144 | 1,171,537,972 | 2,144 |
[
"gpac",
"gpac"
] | [gpac-2.1-DEV-rev48-gf6d6225a-master-x64.exe](https://download.tsi.telecom-paristech.fr/gpac/new_builds/win64/gpac-2.1-DEV-rev48-gf6d6225a-master-x64.exe)
When I open osmo4, it opens a grey window and closes after a few seconds. When opening with a console I see ```[Compositor] OpenGL shaders not supported```. | Opening osmo4 in Win11 VM fails | https://api.github.com/repos/gpac/gpac/issues/2143/comments | 6 | 2022-03-16T09:06:35Z | 2022-11-08T06:25:57Z | https://github.com/gpac/gpac/issues/2143 | 1,170,731,749 | 2,143 |
[
"gpac",
"gpac"
] | I have installed the gpac with exe file from https://gpac.wp.imt.fr/downloads/, and i can find osmo4 player in my computer. now I want play the demo in http://download.tsi.telecom-paristech.fr/gpac/SRD/srd_hevc/multi_rate_p60/ using osmo4. But I can not open or add the file with osmo4 gui. Any idea? thanks a lot. | how to use osmo4 to play a video? | https://api.github.com/repos/gpac/gpac/issues/2142/comments | 7 | 2022-03-16T00:44:39Z | 2022-03-22T07:49:15Z | https://github.com/gpac/gpac/issues/2142 | 1,170,408,302 | 2,142 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | MPD references non-existent initialization segment | https://api.github.com/repos/gpac/gpac/issues/2141/comments | 1 | 2022-03-15T12:53:49Z | 2022-03-22T08:45:49Z | https://github.com/gpac/gpac/issues/2141 | 1,169,636,455 | 2,141 |
[
"gpac",
"gpac"
] | [POC](https://drive.google.com/file/d/19V3_2svctUfavMRpZ6QFgemglsETXXtK/view?usp=sharing)
```
Description
Integer Overflow in MP4Box
Command
MP4Box -bt [POC7](https://drive.google.com/file/d/19V3_2svctUfavMRpZ6QFgemglsETXXtK/view?usp=sharing)
ASAN result
isomedia/box_code_base.c:413:29: runtime error: ... | Integer Overflow or Wraparound | https://api.github.com/repos/gpac/gpac/issues/2140/comments | 1 | 2022-03-14T09:01:56Z | 2022-03-14T15:19:24Z | https://github.com/gpac/gpac/issues/2140 | 1,168,075,634 | 2,140 |
[
"gpac",
"gpac"
] | I already googled-fu it but i found no info about this. | [Question]How to add and/or extract vobsub(idx,sub) files | https://api.github.com/repos/gpac/gpac/issues/2139/comments | 1 | 2022-03-13T21:57:01Z | 2022-03-14T16:25:55Z | https://github.com/gpac/gpac/issues/2139 | 1,167,704,796 | 2,139 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | [BUG] heap-buffer-overflow in gf_base64_encode | https://api.github.com/repos/gpac/gpac/issues/2138/comments | 3 | 2022-03-10T09:47:43Z | 2022-08-03T09:44:25Z | https://github.com/gpac/gpac/issues/2138 | 1,164,990,736 | 2,138 |
[
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC.
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ...).
Hi,
For the provided test input, `MP4Box -bt issue-2137 -std... | Inconsistent/incorrect "fromTo" and "key" values produced by `MP4Box -bt` | https://api.github.com/repos/gpac/gpac/issues/2137/comments | 0 | 2022-03-09T14:18:29Z | 2022-03-09T17:41:29Z | https://github.com/gpac/gpac/issues/2137 | 1,163,998,809 | 2,137 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | GPAC + kvazaar RTMP input works but UDP does not. | https://api.github.com/repos/gpac/gpac/issues/2136/comments | 17 | 2022-03-09T08:55:43Z | 2022-04-23T13:11:41Z | https://github.com/gpac/gpac/issues/2136 | 1,163,659,447 | 2,136 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [ yes] I looked for a similar issue and couldn't find any.
- [yes ] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [yes ] I give en... | a/v sync issue in mp4box converted fragment mp4 | https://api.github.com/repos/gpac/gpac/issues/2135/comments | 8 | 2022-03-08T11:28:09Z | 2022-03-17T12:36:32Z | https://github.com/gpac/gpac/issues/2135 | 1,162,542,633 | 2,135 |
[
"gpac",
"gpac"
] | Hello,
I am building ffmpeg and mp4box with the [ffmpeg-windows-build-helpers](https://github.com/rdp/ffmpeg-windows-build-helpers)
Since recently mp4box building is compromised.
I think it has something to do with a typo in the file `utils/os_file.c`.
There it says in lines 411, 422 and 877: `st.st_mtim.tv_nsec`... | Building of mp4box not working | https://api.github.com/repos/gpac/gpac/issues/2134/comments | 5 | 2022-03-07T14:44:44Z | 2022-03-14T12:44:56Z | https://github.com/gpac/gpac/issues/2134 | 1,161,513,295 | 2,134 |
[
"gpac",
"gpac"
] | POC: https://drive.google.com/file/d/1Iz529FflMClr-NcgRvWSyoPDKbU70dqw/view
```
Command
MP4Box -info POC6
ASAN result
[iso file] Unknown box type url@ in parent dref
[iso file] Unknown box type traj in parent moov
[iso file] Unknown box type 80rak in parent moov
[iso file] Incomplete box mdat - start... | NULL Pointer Dereference | https://api.github.com/repos/gpac/gpac/issues/2133/comments | 0 | 2022-03-07T11:06:17Z | 2022-03-07T13:55:02Z | https://github.com/gpac/gpac/issues/2133 | 1,161,266,778 | 2,133 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC.
- [x] I give enough information for contributors to reproduce my issue (meaningful title, git... | Incorrect result produced by `MP4Box -dxml` | https://api.github.com/repos/gpac/gpac/issues/2132/comments | 0 | 2022-03-05T14:10:05Z | 2022-03-07T14:07:09Z | https://github.com/gpac/gpac/issues/2132 | 1,160,361,817 | 2,132 |
[
"gpac",
"gpac"
] |
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC.
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ...).
Hi,
For the provided test input, `MP4Box -bt issue-2131 ... | Unstable output produced by `MP4Box` | https://api.github.com/repos/gpac/gpac/issues/2131/comments | 0 | 2022-03-03T21:57:45Z | 2022-03-07T13:55:03Z | https://github.com/gpac/gpac/issues/2131 | 1,158,938,281 | 2,131 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Incorrect/inconsistent results produced by `MP4Box -bt` because of uninitialized variable `scheme_type ` in track.c | https://api.github.com/repos/gpac/gpac/issues/2130/comments | 2 | 2022-03-02T16:32:05Z | 2022-03-05T14:03:59Z | https://github.com/gpac/gpac/issues/2130 | 1,157,425,096 | 2,130 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | can gpac transcode one rtmp input to several streams with different resolution and output them with one ll-hls? | https://api.github.com/repos/gpac/gpac/issues/2129/comments | 15 | 2022-02-28T17:19:56Z | 2022-03-21T13:51:13Z | https://github.com/gpac/gpac/issues/2129 | 1,154,352,511 | 2,129 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | How do I modify the value of PART-HOLD-BACK ? | https://api.github.com/repos/gpac/gpac/issues/2128/comments | 2 | 2022-02-27T15:29:45Z | 2022-03-07T19:12:28Z | https://github.com/gpac/gpac/issues/2128 | 1,153,291,255 | 2,128 |
[
"gpac",
"gpac"
] | I'm using 2 MKVs; videos are successfully merged, but without an audiable audio track.
"[NULL] invalid sync code
Appending file X.mkv
No suitable destination track found - creating new one (type vide)
No suitable destination track found - creating new one (type soun)"
This is the only error message I can see.
... | GPAC 2.0 Concat 2 Different Resolutions -> No Audio | https://api.github.com/repos/gpac/gpac/issues/2127/comments | 4 | 2022-02-27T08:33:14Z | 2022-04-12T12:51:39Z | https://github.com/gpac/gpac/issues/2127 | 1,153,049,507 | 2,127 |
[
"gpac",
"gpac"
] | Hello, this is less of an issue and more of a request for some information/assistance. I'd like to see if I can get the OpenXR loader working inside of GPAC's video player to allow a majority of the current VR runtimes (SteamVR, Monado, etc.) to work with GPAC so that non-mobile headsets can be used to watch 360 videos... | OpenXR Implementation for VR Mode (360Videos) | https://api.github.com/repos/gpac/gpac/issues/2126/comments | 5 | 2022-02-24T20:50:09Z | 2022-10-10T17:00:26Z | https://github.com/gpac/gpac/issues/2126 | 1,149,736,410 | 2,126 |
[
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ..... | [2.0.0] Cannot build on Ubuntu and Arch Linux | https://api.github.com/repos/gpac/gpac/issues/2125/comments | 10 | 2022-02-23T13:30:26Z | 2022-02-25T18:36:04Z | https://github.com/gpac/gpac/issues/2125 | 1,148,099,372 | 2,125 |
[
"gpac",
"gpac"
] |
[poc.zip](https://github.com/gpac/gpac/files/8096924/poc.zip)
```
Version:
MP4Box - GPAC version 1.1.0-DEV-rev1762-g90a145735-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your research:
GPAC Filters: https://doi.org/10.1145/3339825.3394... | Heap-based Buffer Overflow | https://api.github.com/repos/gpac/gpac/issues/2124/comments | 0 | 2022-02-18T12:00:23Z | 2022-02-21T08:37:12Z | https://github.com/gpac/gpac/issues/2124 | 1,142,929,565 | 2,124 |
[
"gpac",
"gpac"
] | Hi!
At latest version 1.1.0-DEV-rev1769-g1d936f89d-master.
I tested, but not fixed.
When running #2122 - case-2, number of files grown infinitely.
#2122 - At live mode "muxtype=ts" output file will not remove. - NOT FIXED
Thanks.
-----------------------
Thanks for reporting your issue. Please mak... | #2122 - At live mode "muxtype=ts" output file will not remove. - NOT FIXED | https://api.github.com/repos/gpac/gpac/issues/2123/comments | 1 | 2022-02-18T11:02:55Z | 2022-02-18T12:44:26Z | https://github.com/gpac/gpac/issues/2123 | 1,142,850,357 | 2,123 |
[
"gpac",
"gpac"
] | Hi! Thanks for awesome project.
I found some problem.
At live mode "muxtype=ts" output file will not remove.
# case-1 : muxtype type is not defined : file remove successfully
> gpac flist:srcs=sample.mp4:floop=-1 reframer:rt=on @ -o "http://0.0.0.0:20275/live.mpd:dmode=dynamic:rdirs=/tmp/rdir/0:tsb=1:profil... | At live mode "muxtype=ts" output file will not remove. | https://api.github.com/repos/gpac/gpac/issues/2122/comments | 2 | 2022-02-18T05:09:07Z | 2022-02-18T20:01:33Z | https://github.com/gpac/gpac/issues/2122 | 1,142,367,879 | 2,122 |
[
"gpac",
"gpac"
] | Hi,
Thanks in advance for any help. Please let me know if I should send more information privately.
**Summary**
I had a `sample.mp4` file which has embedded EMSG boxes carrying custom metadata. To serve it via DASH, I used MP4Box to generate the mpd manifest file, and MP4Box generates two files for me
- `samp... | EMSG boxes are lost in fMP4 after MP4Box processing | https://api.github.com/repos/gpac/gpac/issues/2121/comments | 10 | 2022-02-17T08:16:27Z | 2022-02-21T12:25:09Z | https://github.com/gpac/gpac/issues/2121 | 1,141,008,215 | 2,121 |
[
"gpac",
"gpac"
] | ## Description
There is a heap buffer overflow detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1759-geb2d1e6dd-master
```
## Build command
```
./configure --static-mp4box --pre... | There is a heap buffer overflow detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2120/comments | 0 | 2022-02-16T11:57:40Z | 2022-02-16T17:15:45Z | https://github.com/gpac/gpac/issues/2120 | 1,139,917,650 | 2,120 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line .... | gpac generated ll-hls files cannot play normally | https://api.github.com/repos/gpac/gpac/issues/2119/comments | 6 | 2022-02-16T11:22:23Z | 2022-02-18T17:33:27Z | https://github.com/gpac/gpac/issues/2119 | 1,139,883,797 | 2,119 |
[
"gpac",
"gpac"
] | ## Description
There is a heap buffer overflow detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1754-g5430ebe10-master
```
## Build command
```
./configure --static-mp4box --pre... | There is a heap buffer overflow detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2118/comments | 0 | 2022-02-14T07:11:09Z | 2022-02-15T09:42:56Z | https://github.com/gpac/gpac/issues/2118 | 1,136,871,446 | 2,118 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | MP4Box copyright itag doesn't work | https://api.github.com/repos/gpac/gpac/issues/2117/comments | 1 | 2022-02-13T07:18:37Z | 2022-02-13T11:14:08Z | https://github.com/gpac/gpac/issues/2117 | 1,135,375,239 | 2,117 |
[
"gpac",
"gpac"
] | ## Description
There is a heap buffer overflow detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1745-g9e1378706-master
```
## Build command
```
./configure --static-mp4box --pre... | There is a heap buffer overflow detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2116/comments | 0 | 2022-02-10T07:49:52Z | 2022-02-10T20:00:56Z | https://github.com/gpac/gpac/issues/2116 | 1,129,589,949 | 2,116 |
[
"gpac",
"gpac"
] | ## Description
There is a heap buffer overflow detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1745-g9e1378706-master
```
## Build command
```
./configure --static-mp4box --pre... | There is a heap buffer overflow detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2115/comments | 0 | 2022-02-10T07:48:44Z | 2022-02-10T20:00:55Z | https://github.com/gpac/gpac/issues/2115 | 1,129,588,900 | 2,115 |
[
"gpac",
"gpac"
] | ## Description
There is a heap buffer overflow detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1745-g9e1378706-master
```
## Build command
```
./configure --static-mp4box --pre... | There is a heap buffer overflow detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2114/comments | 0 | 2022-02-10T07:47:25Z | 2022-02-10T20:00:55Z | https://github.com/gpac/gpac/issues/2114 | 1,129,587,702 | 2,114 |
[
"gpac",
"gpac"
] | ## Description
There is a segment fault detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1740-gbd98129fd-master
```
## Build command
```
./configure --static-mp4box --prefix=`re... | There is a segment fault detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2113/comments | 0 | 2022-02-09T12:36:07Z | 2022-02-09T14:54:34Z | https://github.com/gpac/gpac/issues/2113 | 1,128,487,015 | 2,113 |
[
"gpac",
"gpac"
] | ## Description
There is a segment fault detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1740-gbd98129fd-master
```
## Build command
```
./configure --static-mp4box --prefix=`re... | There is a segment fault detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2112/comments | 0 | 2022-02-09T12:34:45Z | 2022-02-09T14:54:34Z | https://github.com/gpac/gpac/issues/2112 | 1,128,485,645 | 2,112 |
[
"gpac",
"gpac"
] | ## Description
There is a heap buffer overflow detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1740-gbd98129fd-master
```
## Build command
```
./configure --static-mp4box --pre... | There is a heap buffer overflow detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2111/comments | 0 | 2022-02-09T12:33:29Z | 2022-02-09T14:54:34Z | https://github.com/gpac/gpac/issues/2111 | 1,128,484,064 | 2,111 |
[
"gpac",
"gpac"
] | ## Description
There is a heap buffer overflow detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1740-gbd98129fd-master
```
## Build command
```
./configure --static-mp4box --pre... | There is a heap buffer overflow detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2110/comments | 0 | 2022-02-09T12:32:23Z | 2022-02-09T14:54:34Z | https://github.com/gpac/gpac/issues/2110 | 1,128,482,583 | 2,110 |
[
"gpac",
"gpac"
] | ## Description
There is a use-after-free detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1727-g8be34973d-master
```
## Build command
```
./configure --static-mp4box --prefix=`r... | There is a use-after-free detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2109/comments | 0 | 2022-02-08T04:23:02Z | 2022-02-08T15:23:20Z | https://github.com/gpac/gpac/issues/2109 | 1,126,777,303 | 2,109 |
[
"gpac",
"gpac"
] | ## Description
There is a statck-overflow detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1727-g8be34973d-master
```
## Build command
```
./configure --static-mp4box --prefix=`... | There is a statck-overflow detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2108/comments | 0 | 2022-02-08T04:22:07Z | 2022-02-08T15:23:20Z | https://github.com/gpac/gpac/issues/2108 | 1,126,776,763 | 2,108 |
[
"gpac",
"gpac"
] | ## Description
There is a segment fault detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1727-g8be34973d-master
```
## Build command
```
./configure --static-mp4box --prefix=`re... | There is a segment fault detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2107/comments | 0 | 2022-02-08T04:20:13Z | 2022-02-08T15:23:19Z | https://github.com/gpac/gpac/issues/2107 | 1,126,775,651 | 2,107 |
[
"gpac",
"gpac"
] | ## Description
There is a segment fault detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1727-g8be34973d-master
```
## Build command
```
./configure --static-mp4box --prefix=`re... | There is a segment fault detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2106/comments | 0 | 2022-02-08T04:18:47Z | 2022-02-08T15:23:19Z | https://github.com/gpac/gpac/issues/2106 | 1,126,774,793 | 2,106 |
[
"gpac",
"gpac"
] | ## Description
There is a segment fault detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1727-g8be34973d-master
```
## Build command
```
./configure --static-mp4box --prefix=`re... | There is a segment fault detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2105/comments | 0 | 2022-02-08T04:16:55Z | 2022-02-08T15:23:19Z | https://github.com/gpac/gpac/issues/2105 | 1,126,773,705 | 2,105 |
[
"gpac",
"gpac"
] | ## Description
There is a segment fault detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1727-g8be34973d-master
```
## Build command
```
./configure --static-mp4box --prefix=`re... | There is a segment fault detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2104/comments | 0 | 2022-02-08T04:15:45Z | 2022-02-08T15:23:19Z | https://github.com/gpac/gpac/issues/2104 | 1,126,772,982 | 2,104 |
[
"gpac",
"gpac"
] | ## Description
There is a segment fault detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1727-g8be34973d-master
```
## Build command
```
./configure --static-mp4box --prefix=`re... | There is a segment fault detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2103/comments | 0 | 2022-02-08T04:14:05Z | 2022-02-08T15:23:18Z | https://github.com/gpac/gpac/issues/2103 | 1,126,771,996 | 2,103 |
[
"gpac",
"gpac"
] | ## Description
There is a heap buffer overflow detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1727-g8be34973d-master
```
## Build command
```
./configure --static-mp4box --pre... | There is a heap buffer overflow detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2102/comments | 0 | 2022-02-08T04:12:49Z | 2022-02-08T15:23:18Z | https://github.com/gpac/gpac/issues/2102 | 1,126,771,290 | 2,102 |
[
"gpac",
"gpac"
] | ## Description
There is a heap buffer overflow detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1727-g8be34973d-master
```
## Build command
```
./configure --static-mp4box --pre... | There is a heap buffer overflow detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2101/comments | 0 | 2022-02-08T04:11:25Z | 2022-02-08T15:23:18Z | https://github.com/gpac/gpac/issues/2101 | 1,126,770,464 | 2,101 |
[
"gpac",
"gpac"
] | ## Description
There is a heap buffer overflow detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1727-g8be34973d-master
```
## Build command
```
./configure --static-mp4box --pre... | There is a heap buffer overflow detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2100/comments | 0 | 2022-02-08T04:09:59Z | 2022-02-08T15:23:18Z | https://github.com/gpac/gpac/issues/2100 | 1,126,769,626 | 2,100 |
[
"gpac",
"gpac"
] | Command run:
`gpac --lowlat=no --buffer=8000 -i out/live.mpd#VR @ compositor:fsize=true:sz=true:tvtd=partial @ vout @1 aout`
The test data used is [here](https://www.mediafire.com/file/2r7s1i0tst06ane/out.zip/file)
What happens:
The vout opens a small window, with a content resolution corresponding to the... | Compositor osize not scaling with the viewport | https://api.github.com/repos/gpac/gpac/issues/2099/comments | 1 | 2022-02-07T02:23:15Z | 2022-06-09T11:12:48Z | https://github.com/gpac/gpac/issues/2099 | 1,125,430,301 | 2,099 |
[
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [ ] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/ -- no, because the issue is about compilation.
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github... | compilation on mac os fails after latest change in tinyaes.c | https://api.github.com/repos/gpac/gpac/issues/2098/comments | 2 | 2022-02-04T10:23:25Z | 2022-02-04T15:02:05Z | https://github.com/gpac/gpac/issues/2098 | 1,124,037,091 | 2,098 |
[
"gpac",
"gpac"
] | ## Description
There is a segment fault detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1705-gc3ed3094a-master
```
## Build command
```
./configure --static-mp4box --prefix=`re... | There is a segment fault detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2097/comments | 0 | 2022-02-04T07:29:05Z | 2022-02-04T09:04:42Z | https://github.com/gpac/gpac/issues/2097 | 1,123,896,639 | 2,097 |
[
"gpac",
"gpac"
] | ## Description
There is a segment fault detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1705-gc3ed3094a-master
```
## Build command
```
./configure --static-mp4box --prefix=`re... | There is a segment fault detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2096/comments | 0 | 2022-02-04T07:27:44Z | 2022-02-04T09:04:42Z | https://github.com/gpac/gpac/issues/2096 | 1,123,895,870 | 2,096 |
[
"gpac",
"gpac"
] | ## Description
There is a heap buffer overflow detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1705-gc3ed3094a-master
```
## Build command
```
./configure --static-mp4box --pre... | There is a heap buffer overflow detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2095/comments | 0 | 2022-02-04T07:26:20Z | 2022-02-04T09:04:42Z | https://github.com/gpac/gpac/issues/2095 | 1,123,894,991 | 2,095 |
[
"gpac",
"gpac"
] | ## Description
There is a heap buffer overflow detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1705-gc3ed3094a-master
```
## Build command
```
./configure --static-mp4box --pre... | There is a heap buffer overflow detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2094/comments | 0 | 2022-02-04T07:24:57Z | 2022-02-04T09:04:41Z | https://github.com/gpac/gpac/issues/2094 | 1,123,894,120 | 2,094 |
[
"gpac",
"gpac"
] |
[poc.zip](https://github.com/gpac/gpac/files/7989436/poc.zip)
```
Description
Null Pointer Dereference in afrt_box_read
gdb output
pwndbg> r -bt poc
Starting program: /run/shm/gpac/bin/gcc/MP4Box -bt poc
ERROR: Could not find ELF base!
[Thread debugging using libthread_db enabled]
Using host libthread_... | NULL Pointer Dereference | https://api.github.com/repos/gpac/gpac/issues/2093/comments | 0 | 2022-02-02T19:21:15Z | 2022-02-04T09:04:41Z | https://github.com/gpac/gpac/issues/2093 | 1,122,297,501 | 2,093 |
[
"gpac",
"gpac"
] | [poc.zip](https://github.com/gpac/gpac/files/7978702/poc.zip)
```
Description
Null Pointer Dereference in gitn_box_del
./MP4Box -bt ./poc
Sanitizer output:
AddressSanitizer:DEADLYSIGNAL
=================================================================
==6791==ERROR: AddressSanitizer: SEGV on unknown add... | NULL Pointer Dereference | https://api.github.com/repos/gpac/gpac/issues/2092/comments | 0 | 2022-02-01T13:20:16Z | 2022-02-01T14:29:21Z | https://github.com/gpac/gpac/issues/2092 | 1,120,666,256 | 2,092 |
[
"gpac",
"gpac"
] | ## Description
There is a stack-overflow detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1687-g16bd902cb-master
```
## Build command
```
./configure --static-mp4box --prefix=`r... | There is a stack-overflow detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2091/comments | 0 | 2022-02-01T08:25:03Z | 2022-02-01T14:29:21Z | https://github.com/gpac/gpac/issues/2091 | 1,120,365,859 | 2,091 |
[
"gpac",
"gpac"
] | ## Description
There is a segment fault detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1687-g16bd902cb-master
```
## Build command
```
./configure --static-mp4box --prefix=`re... | There is a segment fault detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2090/comments | 0 | 2022-02-01T08:23:09Z | 2022-02-01T14:29:21Z | https://github.com/gpac/gpac/issues/2090 | 1,120,364,312 | 2,090 |
[
"gpac",
"gpac"
] | ## Description
There is a segment fault detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1687-g16bd902cb-master
```
## Build command
```
./configure --static-mp4box --prefix=`re... | There is a segment fault detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2089/comments | 0 | 2022-02-01T08:21:39Z | 2022-02-01T14:29:20Z | https://github.com/gpac/gpac/issues/2089 | 1,120,363,059 | 2,089 |
[
"gpac",
"gpac"
] | ## Description
There is a segment fault detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1687-g16bd902cb-master
```
## Build command
```
./configure --static-mp4box --prefix=`re... | There is a segment fault detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2088/comments | 0 | 2022-02-01T08:20:09Z | 2022-02-01T14:29:20Z | https://github.com/gpac/gpac/issues/2088 | 1,120,361,825 | 2,088 |
[
"gpac",
"gpac"
] | ## Description
There is a heap buffer overflow detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1687-g16bd902cb-master
```
## Build command
```
./configure --static-mp4box --pre... | There is a heap buffer overflow detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2087/comments | 0 | 2022-02-01T08:18:23Z | 2022-02-01T14:29:19Z | https://github.com/gpac/gpac/issues/2087 | 1,120,360,448 | 2,087 |
[
"gpac",
"gpac"
] | ## Description
There is a heap buffer overflow detected by AddressSanitizer
## System info
```
Ubuntu 20.04.2 LTS
clang version 12.0.0-++20210402082642+04ba60cfe598-1~exp1~20210402063359.71
MP4Box - GPAC version 1.1.0-DEV-rev1687-g16bd902cb-master
```
## Build command
```
./configure --static-mp4box --pre... | There is a heap buffer overflow detected by AddressSanitizer | https://api.github.com/repos/gpac/gpac/issues/2086/comments | 0 | 2022-02-01T08:16:21Z | 2022-02-01T14:29:19Z | https://github.com/gpac/gpac/issues/2086 | 1,120,358,857 | 2,086 |
[
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough inform... | Support drop tile for python API | https://api.github.com/repos/gpac/gpac/issues/2084/comments | 1 | 2022-01-29T22:36:47Z | 2022-02-01T10:12:35Z | https://github.com/gpac/gpac/issues/2084 | 1,118,343,754 | 2,084 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.