cve_id stringlengths 13 16 | cve_published stringlengths 23 23 | cve_descriptions stringlengths 48 2.08k | cve_metrics dict | cve_references listlengths 1 138 | cve_configurations listlengths 1 39 | url stringlengths 37 77 | cve_tags listlengths 1 4 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 88.6k ⌀ | issue_title stringlengths 3 335 | issue_comments_url stringlengths 56 81 | issue_comments_count int64 0 146 | issue_created_at stringlengths 20 20 | issue_updated_at stringlengths 20 20 | issue_html_url stringlengths 37 62 | issue_github_id int64 104M 2.09B | issue_number int64 1 122k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2021-40609 | 2022-06-28T13:15:09.880 | The GetHintFormat function in GPAC 1.0.1 allows attackers to cause a denial of service via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1894"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCC969A1-3F88-40F5-B4A1-54DA05DF081E",
"versionEndExcluding": "2.0.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | https://github.com/gpac/gpac/issues/1894 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] |
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ... | heap-buffer-overflow in MP4BOX at souce file src/isomedia/hint_track.c:46 | https://api.github.com/repos/gpac/gpac/issues/1894/comments | 0 | 2021-08-26T04:44:12Z | 2021-08-30T15:33:44Z | https://github.com/gpac/gpac/issues/1894 | 979,828,664 | 1,894 |
CVE-2021-40943 | 2022-06-28T13:15:09.920 | In Bento4 1.6.0-638, there is a null pointer reference in the function AP4_DescriptorListInspector::Action function in Ap4Descriptor.h:124 , as demonstrated by GPAC. This can cause a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/643"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-638:*:*:*:*:*:*:*",
"matchCriteriaId": "2122DA5E-A523-4D07-B017-982DF2B8B829",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/axiomatic-systems/Bento4/issues/643 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | How to reproduce:
```
1.check out latest code, 5922ba762a
2.compile with asan,
set(CMAKE_C_FLAGS "${CMAKE_C_FLAGS} -fsanitize=address -g")
set(CMAKE_CXX_FLAGS "${CMAKE_CXX_FLAGS} -fsanitize=address -g")
3.run ./mp4dump --verbosity 3 --format text poc
```
You can see the asan information below:
... | Null pointer reference in Ap4Descriptor.h:124 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/643/comments | 0 | 2021-08-25T02:00:03Z | 2021-08-25T02:00:03Z | https://github.com/axiomatic-systems/Bento4/issues/643 | 978,627,371 | 643 |
CVE-2021-40944 | 2022-06-28T13:15:09.963 | In GPAC MP4Box 1.1.0, there is a Null pointer reference in the function gf_filter_pid_get_packet function in src/filter_core/filter_pid.c:5394, as demonstrated by GPAC. This can cause a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1906"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:-:*:*:*:*:*:*",
"matchCriteriaId": "13133329-701B-4D4B-BA02-F2DF80638668",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1906 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Null pointer reference in GPAC at src/filter_core/filter_pid.c:5394 | https://api.github.com/repos/gpac/gpac/issues/1906/comments | 4 | 2021-09-01T07:25:03Z | 2021-09-07T15:18:06Z | https://github.com/gpac/gpac/issues/1906 | 984,803,968 | 1,906 |
CVE-2020-19897 | 2022-06-28T22:15:07.810 | A reflected Cross Site Scripting (XSS) in wuzhicms v4.1.0 allows remote attackers to execute arbitrary web script or HTML via the imgurl parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wuzhicms/wuzhicms/issues/183"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhi_cms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "F4749403-9C42-40DF-A695-A9E31BD37D84",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/wuzhicms/wuzhicms/issues/183 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | A xss vulnerability was discovered in WUZHI CMS 4.1.0
There is a reflected XSS vulnerability which allows remote attackers to inject arbitrary web script or HTML via the imgurl parameter of /index.php?m=core&f=index&_su=wuzhicms.
POC
ji</textarea> <img/src=1 onerror=alert(document.cookie)>
Vulnerability trigg... | wuzhicms v4.1.0 statcode reflected xss vulnerability | https://api.github.com/repos/wuzhicms/wuzhicms/issues/183/comments | 0 | 2019-08-01T08:29:05Z | 2019-08-01T08:30:33Z | https://github.com/wuzhicms/wuzhicms/issues/183 | 475,546,565 | 183 |
CVE-2021-44915 | 2022-07-05T18:15:07.797 | Taocms 3.0.2 was discovered to contain a blind SQL injection vulnerability via the function Edit category. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/taogogo/taocms/issues/8"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:taogogo:taocms:3.0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "AA84748C-B58B-4A72-A527-7FF567BACCC2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | https://github.com/taogogo/taocms/issues/8 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"taogogo",
"taocms"
] | Log in to the background as the default account admin.

We click in order and grab packets:

 | https://api.github.com/repos/taogogo/taocms/issues/8/comments | 0 | 2021-12-07T08:51:23Z | 2021-12-07T08:51:23Z | https://github.com/taogogo/taocms/issues/8 | 1,073,082,158 | 8 |
CVE-2022-32117 | 2022-07-13T21:15:08.123 | Jerryscript v2.4.0 was discovered to contain a stack buffer overflow via the function jerryx_print_unhandled_exception in /util/print.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/5008"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1E97C345-3992-457E-928D-05A0B97B2A5F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/5008 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
0d4969661810b9e618485c284c361e597144e9b9
master
###### Build platform
Ubuntu 16.04.7 LTS (Linux 4.15.0-142-generic x86_64)
###### Build steps
```sh
./tools/build.py --clean --compile-flag=-fsanitize=address --lto=off --error-message=on --profile=es.next --stack-limit=15 --debug --lo... | Stack-buffer-overflow in jerryx_print_unhandled_exception (jerryscript/jerry-ext/util/print.c) | https://api.github.com/repos/jerryscript-project/jerryscript/issues/5008/comments | 1 | 2022-05-29T18:17:00Z | 2022-08-08T06:14:38Z | https://github.com/jerryscript-project/jerryscript/issues/5008 | 1,251,957,111 | 5,008 |
CVE-2022-34027 | 2022-07-18T21:15:07.820 | Nginx NJS v0.7.4 was discovered to contain a segmentation violation via njs_value_property at njs_value.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/504"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.4:*:*:*:*:*:*:*",
"matchCriteriaId": "A12FD5A4-6946-49DD-95D4-154A8DA98F7A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nul... | https://github.com/nginx/njs/issues/504 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nginx",
"njs"
] |
Environment
```OS : Linux ubuntu 5.13.0-27-generic #29~20.04.1-Ubuntu SMP Fri Jan 14 00:32:30 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
Commit : 6cef7f5055ec24275f0ae121c7f8709ff3e0c454
Version : 0.7.4
Build :
./configure --cc=clang --address-sanitizer=YES
make
```
Proof of concept... | SEGV njs_value.c:1083:19 in njs_value_property | https://api.github.com/repos/nginx/njs/issues/504/comments | 0 | 2022-05-19T08:33:21Z | 2022-05-19T23:51:07Z | https://github.com/nginx/njs/issues/504 | 1,241,429,184 | 504 |
CVE-2022-34028 | 2022-07-18T21:15:07.863 | Nginx NJS v0.7.5 was discovered to contain a segmentation violation via njs_utf8_next at src/njs_utf8.h. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/522"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.5:*:*:*:*:*:*:*",
"matchCriteriaId": "295D30FC-8B8F-4DF2-92D8-6AECAF06A01B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nul... | https://github.com/nginx/njs/issues/522 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"nginx",
"njs"
] | Environment
```
Commit : c62a9fb92b102c90a66aa724cb9054183a33a68c
Version : 0.7.5
Build :
./configure --cc=clang --address-sanitizer=YES
make
```
Proof of concept
```
// Minimizing 811225C4-281E-48F6-8D83-E65B5DB8E211
function placeholder(){}
function main() {
var v0 = "WbgAtnLEGv";
v... | SEGV src/njs_utf8.h:52:9 in njs_utf8_next | https://api.github.com/repos/nginx/njs/issues/522/comments | 0 | 2022-06-01T07:38:09Z | 2022-06-04T07:21:08Z | https://github.com/nginx/njs/issues/522 | 1,255,239,687 | 522 |
CVE-2022-34029 | 2022-07-18T21:15:07.910 | Nginx NJS v0.7.4 was discovered to contain an out-of-bounds read via njs_scope_value at njs_scope.h. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.1,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/506"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.4:*:*:*:*:*:*:*",
"matchCriteriaId": "A12FD5A4-6946-49DD-95D4-154A8DA98F7A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nul... | https://github.com/nginx/njs/issues/506 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"nginx",
"njs"
] | Environment
```OS : Linux ubuntu 5.13.0-27-generic #29~20.04.1-Ubuntu SMP Fri Jan 14 00:32:30 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
Commit : 9f4ebc96148308a8ce12f2b54432c87e6d78b881
Version : 0.7.4
Build :
./configure --cc=clang --address-sanitizer=YES
make
```
Proof of concept
``... | SEGV njs_scope.h:74:12 Out-of-bounds Read in njs_scope_value | https://api.github.com/repos/nginx/njs/issues/506/comments | 2 | 2022-05-30T02:09:28Z | 2022-06-02T23:34:07Z | https://github.com/nginx/njs/issues/506 | 1,252,090,775 | 506 |
CVE-2022-34030 | 2022-07-18T21:15:07.953 | Nginx NJS v0.7.5 was discovered to contain a segmentation violation via njs_djb_hash at src/njs_djb_hash.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/540"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.5:*:*:*:*:*:*:*",
"matchCriteriaId": "295D30FC-8B8F-4DF2-92D8-6AECAF06A01B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nul... | https://github.com/nginx/njs/issues/540 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nginx",
"njs"
] | Environment
```OS : Linux ubuntu 5.13.0-27-generic #29~20.04.1-Ubuntu SMP Fri Jan 14 00:32:30 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
Commit : c756e23eb09dac519fe161c88587cc034306630f (high:1882)
Version : 0.7.5
Build :
./configure --cc=clang --address-sanitizer=YES
make
```
Proof of c... | SEGV src/njs_djb_hash.c:21:16 in njs_djb_hash | https://api.github.com/repos/nginx/njs/issues/540/comments | 0 | 2022-06-10T02:31:55Z | 2022-06-11T07:17:08Z | https://github.com/nginx/njs/issues/540 | 1,266,924,732 | 540 |
CVE-2022-34031 | 2022-07-18T21:15:07.997 | Nginx NJS v0.7.5 was discovered to contain a segmentation violation via njs_value_to_number at src/njs_value_conversion.h. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/523"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.5:*:*:*:*:*:*:*",
"matchCriteriaId": "295D30FC-8B8F-4DF2-92D8-6AECAF06A01B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nul... | https://github.com/nginx/njs/issues/523 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nginx",
"njs"
] | Environment
```
Commit : c62a9fb92b102c90a66aa724cb9054183a33a68c
Version : 0.7.5
Build :
./configure --cc=clang --address-sanitizer=YES
make
```
Proof of concept
```
// Minimizing 74595E5A-F4AD-43DB-A4E9-34F2D366AD8A
function placeholder(){}
function main() {
var v0 = /gL8?/;
var v1 ... | SEGV src/njs_value_conversion.h:17:9 in njs_value_to_number | https://api.github.com/repos/nginx/njs/issues/523/comments | 0 | 2022-06-01T07:38:49Z | 2022-06-04T07:21:08Z | https://github.com/nginx/njs/issues/523 | 1,255,241,021 | 523 |
CVE-2022-34032 | 2022-07-18T21:15:08.040 | Nginx NJS v0.7.5 was discovered to contain a segmentation violation in the function njs_value_own_enumerate at src/njs_value.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/524"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.5:*:*:*:*:*:*:*",
"matchCriteriaId": "295D30FC-8B8F-4DF2-92D8-6AECAF06A01B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nul... | https://github.com/nginx/njs/issues/524 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nginx",
"njs"
] | Environment
```
Commit : c62a9fb92b102c90a66aa724cb9054183a33a68c
Version : 0.7.5
Build :
./configure --cc=clang --address-sanitizer=YES
make
```
Proof of concept
```
// Minimizing 9159992D-C762-4DEB-8981-8A3357935A7A
function placeholder(){}
function main() {
var v2 = [];
var v4 = {"... | SEGV src/njs_value.c:240:21 in njs_value_own_enumerate | https://api.github.com/repos/nginx/njs/issues/524/comments | 0 | 2022-06-01T07:39:41Z | 2022-06-09T07:08:06Z | https://github.com/nginx/njs/issues/524 | 1,255,242,842 | 524 |
CVE-2022-34033 | 2022-07-18T21:15:08.083 | HTMLDoc v1.9.15 was discovered to contain a heap overflow via (write_header) /htmldoc/htmldoc/html.cxx:273. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/michaelrsweet/htmldoc/commit/a0014be47d614220db111b360fb6170ef6f3937e"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:htmldoc_project:htmldoc:1.9.15:*:*:*:*:*:*:*",
"matchCriteriaId": "7FA48CA3-3C4E-46CA-8B5E-FDBF99FDD55F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | https://github.com/michaelrsweet/htmldoc/issues/425 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"michaelrsweet",
"htmldoc"
] | AddressSanitizer: heap-buffer-overflow on (write_header) /htmldoc/htmldoc/html.cxx:273 | https://api.github.com/repos/michaelrsweet/htmldoc/issues/425/comments | 3 | 2021-05-06T02:08:38Z | 2021-05-07T10:37:41Z | https://github.com/michaelrsweet/htmldoc/issues/425 | 877,005,444 | 425 | |
CVE-2022-34035 | 2022-07-18T21:15:08.127 | HTMLDoc v1.9.12 and below was discovered to contain a heap overflow via e_node htmldoc/htmldoc/html.cxx:588. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/michaelrsweet/htmldoc/commit/a0014be47d614220db111b360fb6170ef6f3937e"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:htmldoc_project:htmldoc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B9DD956F-44F8-4CB5-B9FD-9269C3E931F2",
"versionEndExcluding": null,
"versionEndIncluding": "1.9.12",
"versionSta... | https://github.com/michaelrsweet/htmldoc/issues/426 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"michaelrsweet",
"htmldoc"
] | Hello, I found a heap-buffer-overflow in write_node
Reporter:
dramthy from Topsec Alpha Lab
test platform:
htmldoc Version :current
OS :Ubuntu 20.04.1 LTS aarch64
kernel: 5.4.0-53-generic
compiler: gcc (Ubuntu 9.3.0-17ubuntu1~20.04) 9.3.0
reproduced:
(htmldoc with asan build option)
./htmldoc-with-as... | AddressSanitizer: heap-buffer-overflow on write_node htmldoc/htmldoc/html.cxx:588 | https://api.github.com/repos/michaelrsweet/htmldoc/issues/426/comments | 2 | 2021-05-07T02:47:11Z | 2021-05-07T10:43:05Z | https://github.com/michaelrsweet/htmldoc/issues/426 | 878,358,961 | 426 |
CVE-2022-34502 | 2022-07-22T15:15:08.703 | Radare2 v5.7.0 was discovered to contain a heap buffer overflow via the function consume_encoded_name_new at format/wasm/wasm.c. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted binary file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/radareorg/radare2/issues/20336"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:radare:radare2:5.7.0:*:*:*:*:*:*:*",
"matchCriteriaId": "C3D7A38B-5772-4F2B-AF10-7C79AF2F18FA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | https://github.com/radareorg/radare2/issues/20336 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"radareorg",
"radare2"
] | ## Environment
```sh
Mon Jun 20 03:01:00 PM CST 2022
radare2 5.7.0 28296 @ linux-x86-64 git.5.7.0
commit: 09569c1d5c324df7f23bdc9ad864ac1c25925745 build: 2022-06-20__11:48:07
Linux x86_64
```
## Description
After 5.7.0 release, a heap buffer overflow can be found in function `consume_encoded_name_new` in ... | heap-buffer-overflow in WASM name handling after 5.7.0 release | https://api.github.com/repos/radareorg/radare2/issues/20336/comments | 2 | 2022-06-20T07:52:24Z | 2023-02-10T00:34:07Z | https://github.com/radareorg/radare2/issues/20336 | 1,276,517,429 | 20,336 |
CVE-2022-34520 | 2022-07-22T15:15:08.827 | Radare2 v5.7.2 was discovered to contain a NULL pointer dereference via the function r_bin_file_xtr_load_buffer at bin/bfile.c. This vulnerability allows attackers to cause a Denial of Service (DOS) via a crafted binary file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/radareorg/radare2/issues/20354"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:radare:radare2:5.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "6E68F1D1-553D-479A-8773-ABCECDD7F1BA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | https://github.com/radareorg/radare2/issues/20354 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"radareorg",
"radare2"
] | ## Environment
```sh
Sat Jun 25 11:13:09 AM CST 2022
radare2 5.7.3 28346 @ linux-x86-64 git.5.6.6-689-gf369ff2de
commit: f369ff2de3c807681ec76df450ee6d4af5e04ce0 build: 2022-06-24__10:39:32
```
## Description
NULL pointer dereference in function `r_bin_file_xtr_load_buffer` in `bin/bfile.c` in Radare2 5.7.... | NULL pointer dereference in `r_bin_file_xtr_load_buffer` | https://api.github.com/repos/radareorg/radare2/issues/20354/comments | 1 | 2022-06-25T03:31:59Z | 2022-06-25T15:08:52Z | https://github.com/radareorg/radare2/issues/20354 | 1,284,427,588 | 20,354 |
CVE-2021-33437 | 2022-07-26T13:15:08.487 | An issue was discovered in mjs (mJS: Restricted JavaScript engine), ES6 (JavaScript version 6). There are memory leaks in frozen_cb() in mjs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "13B1A3EF-A920-4FB4-BD11-F97092B362F7",
"versionEndExcluding": "2.20.0",
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/cesanta/mjs/issues/160 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, mjs (latest master 4c870e5)
Compile Command:
```
$ gcc -fsanitize=address -fno-omit-frame-pointer -DMJS_MAIN mjs.c -ldl -g -o mjs
```
Run Command:
```
$ mjs -f $POC
```
POC file:
https://github.com/Clingto/POC/blob/master/MSA/mjs/mjs-5794-frozen_cb-memor... | AddressSanitizer: 1 memory leaks of frozen_cb() | https://api.github.com/repos/cesanta/mjs/issues/160/comments | 0 | 2021-05-19T08:38:25Z | 2021-05-19T08:38:25Z | https://github.com/cesanta/mjs/issues/160 | 895,159,181 | 160 |
CVE-2021-33438 | 2022-07-26T13:15:08.630 | An issue was discovered in mjs (mJS: Restricted JavaScript engine), ES6 (JavaScript version 6). There is stack buffer overflow in json_parse_array() in mjs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "13B1A3EF-A920-4FB4-BD11-F97092B362F7",
"versionEndExcluding": "2.20.0",
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/cesanta/mjs/issues/158 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, mjs (latest master 4c870e5)
Compile Command:
```
$ gcc -fsanitize=address -fno-omit-frame-pointer -DMJS_MAIN mjs.c -ldl -g -o mjs
```
Run Command:
```
$ mjs -f $POC
```
POC file:
https://github.com/Clingto/POC/blob/master/MSA/mjs/mjs-5fb78-json_parse_arr... | AddressSanitizer: stack-buffer-overflow in json_parse_array() mjs.c:5952 | https://api.github.com/repos/cesanta/mjs/issues/158/comments | 0 | 2021-05-19T08:36:33Z | 2021-05-19T08:36:33Z | https://github.com/cesanta/mjs/issues/158 | 895,156,817 | 158 |
CVE-2021-33439 | 2022-07-26T13:15:08.677 | An issue was discovered in mjs (mJS: Restricted JavaScript engine), ES6 (JavaScript version 6). There is Integer overflow in gc_compact_strings() in mjs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "13B1A3EF-A920-4FB4-BD11-F97092B362F7",
"versionEndExcluding": "2.20.0",
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/cesanta/mjs/issues/159 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, mjs (latest master 4c870e5)
Compile Command:
```
$ gcc -fsanitize=address -fno-omit-frame-pointer -DMJS_MAIN mjs.c -ldl -g -o mjs
```
Run Command:
```
$ mjs -f $POC
```
POC file:
https://github.com/Clingto/POC/blob/master/MSA/mjs/mjs-8d05d-gc_compact_str... | AddressSanitizer: negative-size-param in gc_compact_strings() mjs.c:11575 | https://api.github.com/repos/cesanta/mjs/issues/159/comments | 0 | 2021-05-19T08:37:26Z | 2021-05-19T08:37:26Z | https://github.com/cesanta/mjs/issues/159 | 895,157,862 | 159 |
CVE-2021-33440 | 2022-07-26T13:15:08.717 | An issue was discovered in mjs (mJS: Restricted JavaScript engine), ES6 (JavaScript version 6). There is NULL pointer dereference in mjs_bcode_commit() in mjs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "13B1A3EF-A920-4FB4-BD11-F97092B362F7",
"versionEndExcluding": "2.20.0",
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/cesanta/mjs/issues/163 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, mjs (latest master 4c870e5)
Compile Command:
```
$ gcc -fsanitize=address -fno-omit-frame-pointer -DMJS_MAIN mjs.c -ldl -g -o mjs
```
Run Command:
```
$ mjs -f $POC
```
POC file:
https://github.com/Clingto/POC/blob/master/MSA/mjs/mjs-7954-mjs_bcode_commi... | A NULL pointer dereference in the function mjs_bcode_commit() mjs.c:8051 | https://api.github.com/repos/cesanta/mjs/issues/163/comments | 0 | 2021-05-19T08:40:50Z | 2021-05-19T08:40:50Z | https://github.com/cesanta/mjs/issues/163 | 895,161,871 | 163 |
CVE-2021-33441 | 2022-07-26T13:15:08.757 | An issue was discovered in mjs (mJS: Restricted JavaScript engine), ES6 (JavaScript version 6). There is NULL pointer dereference in exec_expr() in mjs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "13B1A3EF-A920-4FB4-BD11-F97092B362F7",
"versionEndExcluding": "2.20.0",
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/cesanta/mjs/issues/165 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, mjs (latest master 4c870e5)
Compile Command:
```
$ gcc -fsanitize=address -fno-omit-frame-pointer -DMJS_MAIN mjs.c -ldl -g -o mjs
```
Run Command:
```
$ mjs -f $POC
```
POC file:
https://github.com/Clingto/POC/blob/master/MSA/mjs/mjs-9035-exec_expr-null-... | A NULL pointer dereference in the function exec_expr() mjs.c:9144 | https://api.github.com/repos/cesanta/mjs/issues/165/comments | 0 | 2021-05-19T08:42:37Z | 2021-05-19T08:42:37Z | https://github.com/cesanta/mjs/issues/165 | 895,163,896 | 165 |
CVE-2021-33442 | 2022-07-26T13:15:08.803 | An issue was discovered in mjs (mJS: Restricted JavaScript engine), ES6 (JavaScript version 6). There is NULL pointer dereference in json_printf() in mjs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "13B1A3EF-A920-4FB4-BD11-F97092B362F7",
"versionEndExcluding": "2.20.0",
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/cesanta/mjs/issues/161 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, mjs (latest master 4c870e5)
Compile Command:
```
$ gcc -fsanitize=address -fno-omit-frame-pointer -DMJS_MAIN mjs.c -ldl -g -o mjs
```
Run Command:
```
$ mjs -f $POC
```
POC file:
https://github.com/Clingto/POC/blob/master/MSA/mjs/mjs-6368-json_printf-nul... | A NULL pointer dereference in the function json_printf() mjs.c:6396 | https://api.github.com/repos/cesanta/mjs/issues/161/comments | 0 | 2021-05-19T08:39:12Z | 2021-05-19T08:39:12Z | https://github.com/cesanta/mjs/issues/161 | 895,160,290 | 161 |
CVE-2021-33443 | 2022-07-26T13:15:08.847 | An issue was discovered in mjs (mJS: Restricted JavaScript engine), ES6 (JavaScript version 6). There is stack buffer overflow in mjs_execute() in mjs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "13B1A3EF-A920-4FB4-BD11-F97092B362F7",
"versionEndExcluding": "2.20.0",
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/cesanta/mjs/issues/167 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, mjs (latest master 4c870e5)
Compile Command:
```
$ gcc -fsanitize=address -fno-omit-frame-pointer -DMJS_MAIN mjs.c -ldl -g -o mjs
```
Run Command:
```
$ mjs -f $POC
```
POC file:
https://github.com/Clingto/POC/blob/master/MSA/mjs/mjs-9522-mjs_execute-sta... | AddressSanitizer: stack-buffer-overflow in mjs_execute mjs.c:9650 | https://api.github.com/repos/cesanta/mjs/issues/167/comments | 0 | 2021-05-19T08:44:06Z | 2021-05-19T08:44:06Z | https://github.com/cesanta/mjs/issues/167 | 895,165,377 | 167 |
CVE-2021-33444 | 2022-07-26T13:15:08.887 | An issue was discovered in mjs (mJS: Restricted JavaScript engine), ES6 (JavaScript version 6). There is NULL pointer dereference in getprop_builtin_foreign() in mjs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "13B1A3EF-A920-4FB4-BD11-F97092B362F7",
"versionEndExcluding": "2.20.0",
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/cesanta/mjs/issues/166 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, mjs (latest master 4c870e5)
I think it is probably a similar issue as [#114](https://github.com/cesanta/mjs/issues/114)
Compile Command:
```
$ gcc -fsanitize=address -fno-omit-frame-pointer -DMJS_MAIN mjs.c -ldl -g -o mjs
```
Run Command:
```
$ mjs -f $POC... | A NULL pointer dereference in the function getprop_builtin_foreign() mjs.c:9298 | https://api.github.com/repos/cesanta/mjs/issues/166/comments | 0 | 2021-05-19T08:43:21Z | 2021-05-19T08:43:21Z | https://github.com/cesanta/mjs/issues/166 | 895,164,624 | 166 |
CVE-2021-33445 | 2022-07-26T13:15:08.927 | An issue was discovered in mjs (mJS: Restricted JavaScript engine), ES6 (JavaScript version 6). There is NULL pointer dereference in mjs_string_char_code_at() in mjs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "13B1A3EF-A920-4FB4-BD11-F97092B362F7",
"versionEndExcluding": "2.20.0",
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/cesanta/mjs/issues/169 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, mjs (latest master 4c870e5)
Compile Command:
```
$ gcc -fsanitize=address -fno-omit-frame-pointer -DMJS_MAIN mjs.c -ldl -g -o mjs
```
Run Command:
```
$ mjs -f $POC
```
POC file:
https://github.com/Clingto/POC/blob/master/MSA/mjs/mjs-13891-mjs_string_cha... | A NULL pointer dereference in the function mjs_string_char_code_at() mjs.c:14234 | https://api.github.com/repos/cesanta/mjs/issues/169/comments | 0 | 2021-05-19T08:45:40Z | 2021-05-19T08:45:40Z | https://github.com/cesanta/mjs/issues/169 | 895,166,975 | 169 |
CVE-2021-33446 | 2022-07-26T13:15:08.967 | An issue was discovered in mjs (mJS: Restricted JavaScript engine), ES6 (JavaScript version 6). There is NULL pointer dereference in mjs_next() in mjs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "13B1A3EF-A920-4FB4-BD11-F97092B362F7",
"versionEndExcluding": "2.20.0",
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/cesanta/mjs/issues/168 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, mjs (latest master 4c870e5)
I think it is probably a similar issue as [#105](https://github.com/cesanta/mjs/issues/105)
Compile Command:
```
$ gcc -fsanitize=address -fno-omit-frame-pointer -DMJS_MAIN mjs.c -ldl -g -o mjs
```
Run Command:
```
$ mjs -f $POC... | A NULL pointer dereference in the function mjs_next() mjs.c:12512 | https://api.github.com/repos/cesanta/mjs/issues/168/comments | 0 | 2021-05-19T08:44:54Z | 2021-05-19T08:44:54Z | https://github.com/cesanta/mjs/issues/168 | 895,166,227 | 168 |
CVE-2021-33447 | 2022-07-26T13:15:09.003 | An issue was discovered in mjs (mJS: Restricted JavaScript engine), ES6 (JavaScript version 6). There is NULL pointer dereference in mjs_print() in mjs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "13B1A3EF-A920-4FB4-BD11-F97092B362F7",
"versionEndExcluding": "2.20.0",
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/cesanta/mjs/issues/164 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, mjs (latest master 4c870e5)
Compile Command:
```
$ gcc -fsanitize=address -fno-omit-frame-pointer -DMJS_MAIN mjs.c -ldl -g -o mjs
```
Run Command:
```
$ mjs -f $POC
```
POC file:
https://github.com/Clingto/POC/blob/master/MSA/mjs/mjs-7992-mjs_print-null-... | A NULL pointer dereference in the function mjs_print() mjs.c:8085 | https://api.github.com/repos/cesanta/mjs/issues/164/comments | 0 | 2021-05-19T08:41:39Z | 2021-05-19T08:41:39Z | https://github.com/cesanta/mjs/issues/164 | 895,162,768 | 164 |
CVE-2021-33448 | 2022-07-26T13:15:09.043 | An issue was discovered in mjs(mJS: Restricted JavaScript engine), ES6 (JavaScript version 6). There is stack buffer overflow at 0x7fffe9049390. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "13B1A3EF-A920-4FB4-BD11-F97092B362F7",
"versionEndExcluding": "2.20.0",
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/cesanta/mjs/issues/170 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, mjs (latest master 4c870e5)
Compile Command:
```
$ gcc -fsanitize=address -fno-omit-frame-pointer -DMJS_MAIN mjs.c -ldl -g -o mjs
```
Run Command:
```
$ mjs -f $POC
```
POC file:
https://github.com/Clingto/POC/blob/master/MSA/mjs/mjs-module-stack-overflo... | AddressSanitizer: stack-buffer-overflow in <unknown module> | https://api.github.com/repos/cesanta/mjs/issues/170/comments | 0 | 2021-05-19T08:46:26Z | 2021-05-19T08:46:26Z | https://github.com/cesanta/mjs/issues/170 | 895,167,796 | 170 |
CVE-2021-33449 | 2022-07-26T13:15:09.083 | An issue was discovered in mjs (mJS: Restricted JavaScript engine), ES6 (JavaScript version 6). There is NULL pointer dereference in mjs_bcode_part_get_by_offset() in mjs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "13B1A3EF-A920-4FB4-BD11-F97092B362F7",
"versionEndExcluding": "2.20.0",
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/cesanta/mjs/issues/162 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, mjs (latest master 4c870e5)
Compile Command:
```
$ gcc -fsanitize=address -fno-omit-frame-pointer -DMJS_MAIN mjs.c -ldl -g -o mjs
```
Run Command:
```
$ mjs -f $POC
```
POC file:
https://github.com/Clingto/POC/blob/master/MSA/mjs/mjs-7945-mjs_bcode_part_... | A NULL pointer dereference in the function mjs_bcode_part_get_by_offset() mjs.c:8042 | https://api.github.com/repos/cesanta/mjs/issues/162/comments | 0 | 2021-05-19T08:40:02Z | 2021-05-19T08:40:02Z | https://github.com/cesanta/mjs/issues/162 | 895,161,153 | 162 |
CVE-2021-33454 | 2022-07-26T13:15:09.297 | An issue was discovered in yasm version 1.3.0. There is a NULL pointer dereference in yasm_expr_get_intnum() in libyasm/expr.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tortall:yasm:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1453CF78-5025-49BF-A1A6-C62F948B5735",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | https://github.com/yasm/yasm/issues/166 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"yasm",
"yasm"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, yasm (latest master 009450c)
I think it is probably a similar issue as [#83](https://github.com/yasm/yasm/issues/83)
Compile Command:
```
$ ./autogen.sh
make distclean
CC=gcc CXX=g++ CFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" CXXFLAGS="-fsan... | A NULL pointer dereference in the function yasm_expr_get_intnum() libyasm/expr.c:1263 | https://api.github.com/repos/yasm/yasm/issues/166/comments | 4 | 2021-05-19T08:22:19Z | 2024-03-22T14:15:04Z | https://github.com/yasm/yasm/issues/166 | 895,143,168 | 166 |
CVE-2021-33455 | 2022-07-26T13:15:09.337 | An issue was discovered in yasm version 1.3.0. There is a NULL pointer dereference in do_directive() in modules/preprocs/nasm/nasm-pp.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tortall:yasm:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1453CF78-5025-49BF-A1A6-C62F948B5735",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | https://github.com/yasm/yasm/issues/169 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yasm",
"yasm"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, yasm (latest master 009450c)
I think it is probably a similar issue as [#142](https://github.com/yasm/yasm/issues/142)
Compile Command:
```
$ ./autogen.sh
make distclean
CC=gcc CXX=g++ CFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" CXXFLAGS="-fsaniti... | A NULL pointer dereference in the function do_directive() modules/preprocs/nasm/nasm-pp.c:2355 | https://api.github.com/repos/yasm/yasm/issues/169/comments | 1 | 2021-05-19T08:25:00Z | 2024-03-21T11:40:51Z | https://github.com/yasm/yasm/issues/169 | 895,145,758 | 169 |
CVE-2021-33456 | 2022-07-26T13:15:09.377 | An issue was discovered in yasm version 1.3.0. There is a NULL pointer dereference in hash() in modules/preprocs/nasm/nasm-pp.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tortall:yasm:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1453CF78-5025-49BF-A1A6-C62F948B5735",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | https://github.com/yasm/yasm/issues/175 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yasm",
"yasm"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, yasm (latest master 009450c)
Compile Command:
```
$ ./autogen.sh
make distclean
CC=gcc CXX=g++ CFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" CXXFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" ./configure --prefix=$PWD/build --disable-shared
ma... | A NULL pointer dereference in the function hash() modules/preprocs/nasm/nasm-pp.c:1114 | https://api.github.com/repos/yasm/yasm/issues/175/comments | 1 | 2021-05-19T08:30:54Z | 2024-03-21T11:46:29Z | https://github.com/yasm/yasm/issues/175 | 895,151,364 | 175 |
CVE-2021-33457 | 2022-07-26T13:15:09.417 | An issue was discovered in yasm version 1.3.0. There is a NULL pointer dereference in expand_mmac_params() in modules/preprocs/nasm/nasm-pp.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tortall:yasm:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1453CF78-5025-49BF-A1A6-C62F948B5735",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | https://github.com/yasm/yasm/issues/171 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yasm",
"yasm"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, yasm (latest master 009450c)
I think it is probably a similar issue as [#151](https://github.com/yasm/yasm/issues/151)
Compile Command:
```
$ ./autogen.sh
make distclean
CC=gcc CXX=g++ CFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" CXXFLAGS="-fsanit... | A NULL pointer dereference in the function expand_mmac_params() modules/preprocs/nasm/nasm-pp.c:3861 | https://api.github.com/repos/yasm/yasm/issues/171/comments | 2 | 2021-05-19T08:27:21Z | 2024-03-21T11:48:05Z | https://github.com/yasm/yasm/issues/171 | 895,147,985 | 171 |
CVE-2021-33458 | 2022-07-26T13:15:09.457 | An issue was discovered in yasm version 1.3.0. There is a NULL pointer dereference in find_cc() in modules/preprocs/nasm/nasm-pp.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tortall:yasm:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1453CF78-5025-49BF-A1A6-C62F948B5735",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | https://github.com/yasm/yasm/issues/170 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yasm",
"yasm"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, yasm (latest master 009450c)
Compile Command:
```
$ ./autogen.sh
make distclean
CC=gcc CXX=g++ CFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" CXXFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" ./configure --prefix=$PWD/build --disable-shared
ma... | A NULL pointer dereference in the function find_cc() modules/preprocs/nasm/nasm-pp.c:3815 | https://api.github.com/repos/yasm/yasm/issues/170/comments | 1 | 2021-05-19T08:26:28Z | 2024-03-21T12:44:18Z | https://github.com/yasm/yasm/issues/170 | 895,147,145 | 170 |
CVE-2021-33459 | 2022-07-26T13:15:09.500 | An issue was discovered in yasm version 1.3.0. There is a NULL pointer dereference in nasm_parser_directive() in modules/parsers/nasm/nasm-parse.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tortall:yasm:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1453CF78-5025-49BF-A1A6-C62F948B5735",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | https://github.com/yasm/yasm/issues/167 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yasm",
"yasm"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, yasm (latest master 009450c)
Compile Command:
```
$ ./autogen.sh
make distclean
CC=gcc CXX=g++ CFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" CXXFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" ./configure --prefix=$PWD/build --disable-shared
ma... | A NULL pointer dereference in the function nasm_parser_directive() modules/parsers/nasm/nasm-parse.c:1596 | https://api.github.com/repos/yasm/yasm/issues/167/comments | 1 | 2021-05-19T08:23:17Z | 2024-03-21T11:50:13Z | https://github.com/yasm/yasm/issues/167 | 895,144,100 | 167 |
CVE-2021-33460 | 2022-07-26T13:15:09.547 | An issue was discovered in yasm version 1.3.0. There is a NULL pointer dereference in if_condition() in modules/preprocs/nasm/nasm-pp.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tortall:yasm:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1453CF78-5025-49BF-A1A6-C62F948B5735",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | https://github.com/yasm/yasm/issues/168 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yasm",
"yasm"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, yasm (latest master 009450c)
Compile Command:
```
$ ./autogen.sh
make distclean
CC=gcc CXX=g++ CFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" CXXFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" ./configure --prefix=$PWD/build --disable-shared
ma... | A NULL pointer dereference in the function if_condition() modules/preprocs/nasm/nasm-pp.c:2134 | https://api.github.com/repos/yasm/yasm/issues/168/comments | 1 | 2021-05-19T08:24:08Z | 2024-03-21T11:51:21Z | https://github.com/yasm/yasm/issues/168 | 895,144,888 | 168 |
CVE-2021-33461 | 2022-07-26T13:15:09.590 | An issue was discovered in yasm version 1.3.0. There is a use-after-free in yasm_intnum_destroy() in libyasm/intnum.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tortall:yasm:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1453CF78-5025-49BF-A1A6-C62F948B5735",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | https://github.com/yasm/yasm/issues/161 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yasm",
"yasm"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, yasm (latest master 009450c)
I think it is probably a similar issue as [#149](https://github.com/yasm/yasm/issues/149)
Compile Command:
```
$ ./autogen.sh
make distclean
CC=gcc CXX=g++ CFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" CXXFLAGS="-fsanit... | AddressSanitizer: heap-use-after-free in yasm_intnum_destroy() libyasm/intnum.c:415 | https://api.github.com/repos/yasm/yasm/issues/161/comments | 3 | 2021-05-19T08:15:14Z | 2024-03-21T11:56:29Z | https://github.com/yasm/yasm/issues/161 | 895,135,903 | 161 |
CVE-2021-33462 | 2022-07-26T13:15:09.647 | An issue was discovered in yasm version 1.3.0. There is a use-after-free in expr_traverse_nodes_post() in libyasm/expr.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tortall:yasm:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1453CF78-5025-49BF-A1A6-C62F948B5735",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | https://github.com/yasm/yasm/issues/165 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yasm",
"yasm"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, yasm (latest master 009450c)
I think it is probably a similar issue as [#126](https://github.com/yasm/yasm/issues/126
)
Compile Command:
```
$ ./autogen.sh
make distclean
CC=gcc CXX=g++ CFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" CXXFLAGS="-fsa... | AddressSanitizer: heap-use-after-free in expr_traverse_nodes_post() libyasm/expr.c:1112 | https://api.github.com/repos/yasm/yasm/issues/165/comments | 1 | 2021-05-19T08:21:12Z | 2024-03-21T12:28:49Z | https://github.com/yasm/yasm/issues/165 | 895,142,015 | 165 |
CVE-2021-33463 | 2022-07-26T13:15:09.687 | An issue was discovered in yasm version 1.3.0. There is a NULL pointer dereference in yasm_expr__copy_except() in libyasm/expr.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tortall:yasm:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1453CF78-5025-49BF-A1A6-C62F948B5735",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | https://github.com/yasm/yasm/issues/174 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yasm",
"yasm"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, yasm (latest master 009450c)
Compile Command:
```
$ ./autogen.sh
make distclean
CC=gcc CXX=g++ CFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" CXXFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" ./configure --prefix=$PWD/build --disable-shared
ma... | A NULL pointer dereference in the function yasm_expr__copy_except() libyasm/expr.c:999 | https://api.github.com/repos/yasm/yasm/issues/174/comments | 2 | 2021-05-19T08:30:07Z | 2024-03-22T14:00:39Z | https://github.com/yasm/yasm/issues/174 | 895,150,639 | 174 |
CVE-2021-33464 | 2022-07-26T13:15:09.730 | An issue was discovered in yasm version 1.3.0. There is a heap-buffer-overflow in inc_fopen() in modules/preprocs/nasm/nasm-pp.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tortall:yasm:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1453CF78-5025-49BF-A1A6-C62F948B5735",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | https://github.com/yasm/yasm/issues/164 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yasm",
"yasm"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, yasm (latest master 009450c)
Compile Command:
```
$ ./autogen.sh
make distclean
CC=gcc CXX=g++ CFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" CXXFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" ./configure --prefix=$PWD/build --disable-shared
ma... | AddressSanitizer: heap-buffer-overflow in inc_fopen() modules/preprocs/nasm/nasm-pp.c:1835 | https://api.github.com/repos/yasm/yasm/issues/164/comments | 4 | 2021-05-19T08:20:09Z | 2022-12-14T17:47:19Z | https://github.com/yasm/yasm/issues/164 | 895,140,978 | 164 |
CVE-2021-33465 | 2022-07-26T13:15:09.773 | An issue was discovered in yasm version 1.3.0. There is a NULL pointer dereference in expand_mmacro() in modules/preprocs/nasm/nasm-pp.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tortall:yasm:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1453CF78-5025-49BF-A1A6-C62F948B5735",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | https://github.com/yasm/yasm/issues/173 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yasm",
"yasm"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, yasm (latest master 009450c)
Compile Command:
```
$ ./autogen.sh
make distclean
CC=gcc CXX=g++ CFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" CXXFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" ./configure --prefix=$PWD/build --disable-shared
ma... | A NULL pointer dereference in the function expand_mmacro() modules/preprocs/nasm/nasm-pp.c:4764 | https://api.github.com/repos/yasm/yasm/issues/173/comments | 1 | 2021-05-19T08:29:17Z | 2024-03-21T12:35:36Z | https://github.com/yasm/yasm/issues/173 | 895,149,848 | 173 |
CVE-2021-33466 | 2022-07-26T13:15:09.817 | An issue was discovered in yasm version 1.3.0. There is a NULL pointer dereference in expand_smacro() in modules/preprocs/nasm/nasm-pp.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tortall:yasm:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1453CF78-5025-49BF-A1A6-C62F948B5735",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | https://github.com/yasm/yasm/issues/172 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yasm",
"yasm"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, yasm (latest master 009450c)
I think it is probably a similar issue as [#142](https://github.com/yasm/yasm/issues/142)
Compile Command:
```
$ ./autogen.sh
make distclean
CC=gcc CXX=g++ CFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" CXXFLAGS="-fsanit... | A NULL pointer dereference in the function expand_smacro() modules/preprocs/nasm/nasm-pp.c:4229 | https://api.github.com/repos/yasm/yasm/issues/172/comments | 1 | 2021-05-19T08:28:18Z | 2024-03-21T12:36:44Z | https://github.com/yasm/yasm/issues/172 | 895,148,925 | 172 |
CVE-2021-33467 | 2022-07-26T13:15:09.860 | An issue was discovered in yasm version 1.3.0. There is a use-after-free in pp_getline() in modules/preprocs/nasm/nasm-pp.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tortall:yasm:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1453CF78-5025-49BF-A1A6-C62F948B5735",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | https://github.com/yasm/yasm/issues/163 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yasm",
"yasm"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, yasm (latest master 009450c)
Compile Command:
```
$ ./autogen.sh
make distclean
CC=gcc CXX=g++ CFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" CXXFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" ./configure --prefix=$PWD/build --disable-shared
ma... | AddressSanitizer: heap-use-after-free in pp_getline() modules/preprocs/nasm/nasm-pp.c:5024 | https://api.github.com/repos/yasm/yasm/issues/163/comments | 1 | 2021-05-19T08:19:19Z | 2024-03-21T12:37:57Z | https://github.com/yasm/yasm/issues/163 | 895,140,170 | 163 |
CVE-2021-33468 | 2022-07-26T13:15:09.903 | An issue was discovered in yasm version 1.3.0. There is a use-after-free in error() in modules/preprocs/nasm/nasm-pp.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tortall:yasm:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1453CF78-5025-49BF-A1A6-C62F948B5735",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | https://github.com/yasm/yasm/issues/162 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yasm",
"yasm"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, yasm (latest master 009450c)
Compile Command:
```
$ ./autogen.sh
make distclean
CC=gcc CXX=g++ CFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" CXXFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" ./configure --prefix=$PWD/build --disable-shared
ma... | AddressSanitizer: heap-use-after-free in error() modules/preprocs/nasm/nasm-pp.c:4830 | https://api.github.com/repos/yasm/yasm/issues/162/comments | 1 | 2021-05-19T08:17:11Z | 2024-03-21T12:39:00Z | https://github.com/yasm/yasm/issues/162 | 895,137,925 | 162 |
CVE-2022-34121 | 2022-07-27T18:15:09.313 | Cuppa CMS v1.0 was discovered to contain a local file inclusion (LFI) vulnerability via the component /templates/default/html/windows/right.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/CuppaCMS/CuppaCMS/issues/18"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/hansmach1ne/MyExpl... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cuppacms:cuppacms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "983E1279-93C7-47D9-9AC8-EFB6D57B92E7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | https://github.com/CuppaCMS/CuppaCMS/issues/18 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"CuppaCMS",
"CuppaCMS"
] | Cuppa CMS suffers from local file inclusion vulnerability in '/templates/default/html/windows/right.php' script using $_POST['url'] parameter.
Using the following exploit it is possible to include arbitrary server file:
curl -X POST "http://IP/cuppa/templates/default/html/windows/right.php" -d "url=../../../../../.... | Non-authenticated Local File Inclusion vulnerability in CuppaCMS templates | https://api.github.com/repos/CuppaCMS/CuppaCMS/issues/18/comments | 2 | 2022-01-06T22:53:08Z | 2023-11-14T23:17:05Z | https://github.com/CuppaCMS/CuppaCMS/issues/18 | 1,095,777,063 | 18 |
CVE-2022-34928 | 2022-08-03T01:15:07.397 | JFinal CMS v5.1.0 was discovered to contain a SQL injection vulnerability via /system/user. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jflyfox/jfinal_cms/issues/43"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jflyfox:jfinal_cms:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9B33E946-BD15-449C-B736-013773A64DF6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/jflyfox/jfinal_cms/issues/43 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jflyfox",
"jfinal_cms"
] | There is a SQLI vul in background mode.The route is as following
<img width="910" alt="1" src="https://user-images.githubusercontent.com/58795040/175862384-81e6d16e-8c57-493c-a73b-294ef4deb3d3.png">
vulnerable argument passing is as following
<img width="713" alt="2" src="https://user-images.githubusercontent.com/... | jfinal_ CMS 5.1.0 SQL injection | https://api.github.com/repos/jflyfox/jfinal_cms/issues/43/comments | 0 | 2022-06-27T04:58:14Z | 2022-06-27T04:58:14Z | https://github.com/jflyfox/jfinal_cms/issues/43 | 1,285,238,213 | 43 |
CVE-2022-36262 | 2022-08-15T12:15:20.673 | An issue was discovered in taocms 3.0.2. in the website settings that allows arbitrary php code to be injected by modifying config.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"URL Repurposed"
],
"url": "http://taocms.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/taogogo/taocms"
},
{
"source": "cve... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:taogogo:taocms:3.0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "AA84748C-B58B-4A72-A527-7FF567BACCC2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | https://github.com/taogogo/taocms/issues/34 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"taogogo",
"taocms"
] | 1. We enter the management page, Go to website settings.

2. Next, I want to inject php code by modifying these settings.
From the config.php file we found that the modified configuration will be writte... | Bypass security protection injection code in the website settings function | https://api.github.com/repos/taogogo/taocms/issues/34/comments | 0 | 2022-07-17T03:21:56Z | 2022-07-17T03:21:56Z | https://github.com/taogogo/taocms/issues/34 | 1,306,974,846 | 34 |
CVE-2022-36262 | 2022-08-15T12:15:20.673 | An issue was discovered in taocms 3.0.2. in the website settings that allows arbitrary php code to be injected by modifying config.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"URL Repurposed"
],
"url": "http://taocms.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/taogogo/taocms"
},
{
"source": "cve... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:taogogo:taocms:3.0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "AA84748C-B58B-4A72-A527-7FF567BACCC2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | https://github.com/taogogo/taocms/issues/34?by=xboy%28topsec%29 | null | github.com | [
"taogogo",
"taocms"
] | 1. We enter the management page, Go to website settings.

2. Next, I want to inject php code by modifying these settings.
From the config.php file we found that the modified configuration will be writte... | Bypass security protection injection code in the website settings function | https://api.github.com/repos/taogogo/taocms/issues/34/comments | 0 | 2022-07-17T03:21:56Z | 2022-07-17T03:21:56Z | https://github.com/taogogo/taocms/issues/34 | 1,306,974,846 | 34 |
CVE-2022-35100 | 2022-08-16T21:15:10.973 | SWFTools commit 772e55a2 was discovered to contain a segmentation violation via gfxline_getbbox at /lib/gfxtools.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/182"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:-:*:*:*:*:*:*:*",
"matchCriteriaId": "05E27E60-6223-457B-BF90-E747C9C5DEE1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/matthiaskramm/swftools/issues/182 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | Hi, I currently learn to use fuzz tech to detect bugs and I found something in this repo.
in order to reproduce the crash info, please attach ASAN when you compile this repo.
## heap buffer overflow
### reproduce
command to reproduce: ./pdf2swf -G -f -t [sample file] -o /dev/null
### sample file
[id3_he... | bug found in swftools-pdf2swf | https://api.github.com/repos/swftools/swftools/issues/182/comments | 0 | 2022-07-03T08:46:34Z | 2022-07-04T03:25:22Z | https://github.com/swftools/swftools/issues/182 | 1,292,246,190 | 182 |
CVE-2022-35105 | 2022-08-16T21:15:11.107 | SWFTools commit 772e55a2 was discovered to contain a heap-buffer overflow via /bin/png2swf+0x552cea. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/183"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:-:*:*:*:*:*:*:*",
"matchCriteriaId": "05E27E60-6223-457B-BF90-E747C9C5DEE1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/matthiaskramm/swftools/issues/183 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | Hi, I currently learn to use fuzz tech to detect bugs and I found something in this repo.
in order to reproduce the crash info, please attach ASAN when you compile this repo.
## heap buffer overflow
### reproduce
command to reproduce the crash : ./png2swf -j 50 [sample file] -o /dev/null
### sample file
[id... | bug found in swftools-png2swf | https://api.github.com/repos/swftools/swftools/issues/183/comments | 0 | 2022-07-03T08:51:23Z | 2022-07-04T03:22:44Z | https://github.com/swftools/swftools/issues/183 | 1,292,247,150 | 183 |
CVE-2022-35107 | 2022-08-16T21:15:11.180 | SWFTools commit 772e55a2 was discovered to contain a stack overflow via vfprintf at /stdio-common/vfprintf.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/184"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:-:*:*:*:*:*:*:*",
"matchCriteriaId": "05E27E60-6223-457B-BF90-E747C9C5DEE1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/matthiaskramm/swftools/issues/184 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | # heap buffer overflow
### reproduce
command to reproduce: ./pdf2swf -G -f -t [sample file] -o /dev/null
### sample file
[id458_heap_overflow_draw_stroke.zip](https://github.com/matthiaskramm/swftools/files/9036118/id458_heap_overflow_draw_stroke.zip)
### crash info
```
==11942==ERROR: AddressSanitizer: heap-b... | bug report swftools-pdf2swf | https://api.github.com/repos/swftools/swftools/issues/184/comments | 0 | 2022-07-04T03:13:51Z | 2022-07-04T03:20:37Z | https://github.com/swftools/swftools/issues/184 | 1,292,557,716 | 184 |
CVE-2022-35113 | 2022-08-16T21:15:11.363 | SWFTools commit 772e55a2 was discovered to contain a heap-buffer overflow via swf_DefineLosslessBitsTagToImage at /modules/swfbits.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/185"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:-:*:*:*:*:*:*:*",
"matchCriteriaId": "05E27E60-6223-457B-BF90-E747C9C5DEE1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/matthiaskramm/swftools/issues/185 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | # swfrender
## heap buffer overflow
### command to reproduce
`./swfrender [sample file] -o /dev/null`
### crash sample
[id8_heap-buffer-overflow_swf_DefineLosslessBitsTagToImage.zip](https://github.com/matthiaskramm/swftools/files/9036326/id8_heap-buffer-overflow_swf_DefineLosslessBitsTagToImage.zip)
### cr... | bug found in swfrender | https://api.github.com/repos/swftools/swftools/issues/185/comments | 0 | 2022-07-04T04:15:24Z | 2022-07-04T04:15:24Z | https://github.com/swftools/swftools/issues/185 | 1,292,592,670 | 185 |
CVE-2022-35433 | 2022-08-16T21:15:11.440 | ffjpeg commit caade60a69633d74100bd3c2528bddee0b6a1291 was discovered to contain a memory leak via /src/jfif.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/rockcarry/ffjpeg/issues/52"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ffjpeg_project:ffjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A1391A61-FDE9-48B2-A3F5-5A162BA44F82",
"versionEndExcluding": "2021-12-16",
"versionEndIncluding": null,
"versionS... | https://github.com/rockcarry/ffjpeg/issues/52 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"rockcarry",
"ffjpeg"
] | ### sample file
[id8_memory_leak.zip](https://github.com/rockcarry/ffjpeg/files/9053199/id8_memory_leak.zip)
### command to reproduce
`./ffjpeg -d [sample file]`
### execute info
```
usrc overflow
=================================================================
==16225==ERROR: LeakSanitizer: detected me... | memory leak | https://api.github.com/repos/rockcarry/ffjpeg/issues/52/comments | 1 | 2022-07-06T08:50:43Z | 2023-07-13T01:47:45Z | https://github.com/rockcarry/ffjpeg/issues/52 | 1,295,485,297 | 52 |
CVE-2022-36186 | 2022-08-17T15:15:08.480 | A Null Pointer dereference vulnerability exists in GPAC 2.1-DEV-revUNKNOWN-master via the function gf_filter_pid_set_property_full () at filter_core/filter_pid.c:5250,which causes a Denial of Service (DoS). This vulnerability was fixed in commit b43f9d1. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2223"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.1:dev:*:*:*:*:*:*",
"matchCriteriaId": "2963671B-FA29-45DB-80B0-92F9E55F5159",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/2223 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [ ] I looked for a similar issue and couldn't find any.
- [ ] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ ] I give enough info... | A NULL pointer dereference in gf_filter_pid_set_property_full | https://api.github.com/repos/gpac/gpac/issues/2223/comments | 0 | 2022-07-07T10:26:55Z | 2022-07-12T17:13:11Z | https://github.com/gpac/gpac/issues/2223 | 1,297,164,642 | 2,223 |
CVE-2022-36190 | 2022-08-17T15:15:08.543 | GPAC mp4box 2.1-DEV-revUNKNOWN-master has a use-after-free vulnerability in function gf_isom_dovi_config_get. This vulnerability was fixed in commit fef6242. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2220"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | https://github.com/gpac/gpac/issues/2220 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [ ] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Heap Use After Free in function gf_isom_dovi_config_get | https://api.github.com/repos/gpac/gpac/issues/2220/comments | 1 | 2022-07-06T03:36:02Z | 2022-07-12T17:13:50Z | https://github.com/gpac/gpac/issues/2220 | 1,295,074,577 | 2,220 |
CVE-2022-36191 | 2022-08-17T16:15:07.920 | A heap-buffer-overflow had occurred in function gf_isom_dovi_config_get of isomedia/avc_ext.c:2490, as demonstrated by MP4Box. This vulnerability was fixed in commit fef6242. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2218"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | https://github.com/gpac/gpac/issues/2218 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [ ] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | heap-buffer-overflow in function gf_isom_dovi_config_get | https://api.github.com/repos/gpac/gpac/issues/2218/comments | 0 | 2022-07-04T10:10:00Z | 2022-07-12T17:13:10Z | https://github.com/gpac/gpac/issues/2218 | 1,292,941,893 | 2,218 |
CVE-2022-35164 | 2022-08-18T05:15:07.603 | LibreDWG v0.12.4.4608 & commit f2dea29 was discovered to contain a heap use-after-free via bit_copy_chain. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/497"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0A8152A2-6867-4B31-8F47-A1A655A49EFF",
"versionEndExcluding": "0.12.4.4608",
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/LibreDWG/libredwg/issues/497 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | # Vulnerability description
version: [0.12.4.4608](https://github.com/LibreDWG/libredwg/releases/tag/0.12.4.4608) & latest commit [f2dea29](https://github.com/LibreDWG/libredwg/commit/f2dea296a0a3bb16afdae8d2ca16749a617a4383)
poc: [poc](https://github.com/0xdd96/PoC/raw/main/libredwg/UAF-bit_copy_chain)
command: ./... | Heap use-after-free still exists in the bit_copy_chain | https://api.github.com/repos/LibreDWG/libredwg/issues/497/comments | 2 | 2022-06-17T12:04:26Z | 2023-06-27T10:19:27Z | https://github.com/LibreDWG/libredwg/issues/497 | 1,274,949,181 | 497 |
CVE-2022-35165 | 2022-08-18T05:15:07.657 | An issue in AP4_SgpdAtom::AP4_SgpdAtom() of Bento4-1.6.0-639 allows attackers to cause a Denial of Service (DoS) via a crafted mp4 input. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/712"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/axiomatic-systems/Bento4/issues/712 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # Vulnerability description
**version:** Bento4-1.6.0-639
**command:** ./mp42aac $POC /dev/null
**Download:** [poc](https://github.com/0xdd96/PoC/raw/main/Bento4/AP4_SgpdAtom::AP4_SgpdAtom-out-of-memory)
Here is the trace reported by ASAN:
```
$ mp42aac poc /dev/null
AddressSanitizer: Out of memory. The proc... | Possible memory exhuastion in AP4_SgpdAtom::AP4_SgpdAtom(). The process has exhausted 65536MB memory. | https://api.github.com/repos/axiomatic-systems/Bento4/issues/712/comments | 0 | 2022-05-31T14:44:43Z | 2022-06-04T17:16:23Z | https://github.com/axiomatic-systems/Bento4/issues/712 | 1,253,977,287 | 712 |
CVE-2022-35166 | 2022-08-18T05:15:07.700 | libjpeg commit 842c7ba was discovered to contain an infinite loop via the component JPEG::ReadInternal. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/76"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:2022-06-15:*:*:*:*:*:*:*",
"matchCriteriaId": "CDECFA58-57FC-4227-A771-A74B47C7C502",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/thorfdbg/libjpeg/issues/76 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | **version:** latest commit https://github.com/thorfdbg/libjpeg/commit/842c7baef7808f12cad19b49b2efcfa9575dbc78
**poc:** [poc](https://github.com/0xdd96/PoC/raw/main/libjpeg/infinite-loop-ReadInternal)
**command:** ./jpeg poc /dev/null
Here is the backtrace in GDB:
```
pwndbg> backtrace
#0 0x000055555558fa8a in... | Infinite loop in JPEG::ReadInternal | https://api.github.com/repos/thorfdbg/libjpeg/issues/76/comments | 1 | 2022-06-26T04:17:35Z | 2022-06-27T18:59:25Z | https://github.com/thorfdbg/libjpeg/issues/76 | 1,284,796,852 | 76 |
CVE-2022-35173 | 2022-08-18T06:15:07.280 | An issue was discovered in Nginx NJS v0.7.5. The JUMP offset for a break instruction was not set to a correct offset during code generation, leading to a segmentation violation. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "http://hg.nginx.org/njs/rev/b7c4e0f714a9"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/commit/40455389679... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nginx:njs:0.7.5:*:*:*:*:*:*:*",
"matchCriteriaId": "AFF53793-2148-4A4F-AA75-6D9B959E9B7A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/nginx/njs/issues/553 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nginx",
"njs"
] | Hi, the following PoC triggers a crash (related to string fmt?) in the latest commit.
```js
(function() {
while ([])
try {
break
try {
return } catch (a) {}
} catch (b) {}
}())
```
Environment:
```
Commit: e008f7ae22834ff1173b7a0067b14c821102018d
System: Ubuntu 18.04.6 LTS
`... | SEGV in njs_sprintf.c:424:19 | https://api.github.com/repos/nginx/njs/issues/553/comments | 0 | 2022-06-20T21:18:10Z | 2024-07-20T00:35:11Z | https://github.com/nginx/njs/issues/553 | 1,277,395,914 | 553 |
CVE-2020-27787 | 2022-08-18T19:15:14.210 | A Segmentaation fault was found in UPX in invert_pt_dynamic() function in p_lx_elf.cpp. An attacker with a crafted input file allows invalid memory address access that could lead to a denial of service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/commit/e2f60adc95334f47e286838dac33160819c5d74d"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2A4A2432-18AE-4B27-A527-030DD9D34F93",
"versionEndExcluding": "3.96",
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/upx/upx/issues/333 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | ## Environment
A crafted input will lead to crash in p_lx_elf.cpp at UPX 3.96(latest version,git clone from branch devel)
upx 3.96-git-1bb93d4fce9f+
UCL data compression library 1.03
zlib data compression library 1.2.8
LZMA SDK version 4.43
Copyright (C) 1996-2020 Markus Franz Xaver Johannes Oberhumer
Copyrigh... | Segmentation fault in PackLinuxElf64::invert_pt_dynamic at p_lx_elf.cpp:5173 | https://api.github.com/repos/upx/upx/issues/333/comments | 4 | 2020-01-14T07:02:22Z | 2022-08-18T21:41:23Z | https://github.com/upx/upx/issues/333 | 549,373,236 | 333 |
CVE-2020-27790 | 2022-08-18T19:15:14.270 | A floating point exception issue was discovered in UPX in PackLinuxElf64::invert_pt_dynamic() function of p_lx_elf.cpp file. An attacker with a crafted input file could trigger this issue that could cause a crash leading to a denial of service. The highest impact is to Availability. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/commit/eb90eab6325d009004ffb155e3e33f22d4d3ca26"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2A4A2432-18AE-4B27-A527-030DD9D34F93",
"versionEndExcluding": "3.96",
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/upx/upx/issues/331 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | ## The environment
A crafted input will lead to crash in p_lx_elf.cpp at UPX 3.96(latest version,git clone from branch devel)
root@ubuntu:/home/upx_cp_2/src# ./upx.out --version
upx 3.96-git-0f4975fd7ffb+
UCL data compression library 1.03
zlib data compression library 1.2.8
LZMA SDK version 4.43
Copyright (C) ... | SIGFPE divide by zero in PackLinuxElf64::invert_pt_dynamic at p_lx_elf.cpp:5108 | https://api.github.com/repos/upx/upx/issues/331/comments | 2 | 2020-01-13T07:11:42Z | 2022-08-18T21:42:09Z | https://github.com/upx/upx/issues/331 | 548,744,640 | 331 |
CVE-2020-27788 | 2022-08-18T20:15:08.947 | An out-of-bounds read access vulnerability was discovered in UPX in PackLinuxElf64::canPack() function of p_lx_elf.cpp file. An attacker with a crafted input file could trigger this issue that could cause a crash leading to a denial of service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/commit/1bb93d4fce9f1d764ba57bf5ac154af515b3fc83"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2A4A2432-18AE-4B27-A527-030DD9D34F93",
"versionEndExcluding": "3.96",
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/upx/upx/issues/332 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | ## Environment
A crafted input will lead to crash in p_lx_elf.cpp at UPX 3.96(latest version,git clone from branch devel)
root@ubuntu:/home/upx_cp_2/src# ./upx.out --version
upx 3.96-git-0f4975fd7ffb+
UCL data compression library 1.03
zlib data compression library 1.2.8
LZMA SDK version 4.43
Copyright (C) 1996... | heap-buffer-overflow in PackLinuxElf64::canPack() at p_lx_elf.cpp:2385 | https://api.github.com/repos/upx/upx/issues/332/comments | 2 | 2020-01-13T08:10:55Z | 2022-08-18T22:37:18Z | https://github.com/upx/upx/issues/332 | 548,768,610 | 332 |
CVE-2022-37047 | 2022-08-18T20:15:11.837 | The component tcprewrite in Tcpreplay v4.4.1 was discovered to contain a heap-based buffer overflow in get_ipv6_next at common/get.c:713. NOTE: this is different from CVE-2022-27940. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/734"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "820B7B7A-25F9-42C6-B0B0-0A2A34648477",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/appneta/tcpreplay/issues/734 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | You are opening a _bug report_ against the Tcpreplay project: we use
GitHub Issues for tracking bug reports and feature requests.
If you have a question about how to use Tcpreplay, you are at the wrong
site. You can ask a question on the [tcpreplay-users mailing list](https://sourceforge.net/p/tcpreplay/mailman/tc... | [Bug] heap-overflow in get.c:713 | https://api.github.com/repos/appneta/tcpreplay/issues/734/comments | 1 | 2022-07-24T02:43:39Z | 2022-08-07T02:02:04Z | https://github.com/appneta/tcpreplay/issues/734 | 1,315,792,459 | 734 |
CVE-2022-37048 | 2022-08-18T20:15:11.880 | The component tcprewrite in Tcpreplay v4.4.1 was discovered to contain a heap-based buffer overflow in get_l2len_protocol at common/get.c:344. NOTE: this is different from CVE-2022-27941. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/735"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "820B7B7A-25F9-42C6-B0B0-0A2A34648477",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/appneta/tcpreplay/issues/735 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | You are opening a _bug report_ against the Tcpreplay project: we use
GitHub Issues for tracking bug reports and feature requests.
If you have a question about how to use Tcpreplay, you are at the wrong
site. You can ask a question on the [tcpreplay-users mailing list](https://sourceforge.net/p/tcpreplay/mailman/tc... | [Bug] heap-overflow in get.c:344 | https://api.github.com/repos/appneta/tcpreplay/issues/735/comments | 1 | 2022-07-24T07:35:35Z | 2022-08-07T02:55:11Z | https://github.com/appneta/tcpreplay/issues/735 | 1,315,833,757 | 735 |
CVE-2022-37049 | 2022-08-18T20:15:11.927 | The component tcpprep in Tcpreplay v4.4.1 was discovered to contain a heap-based buffer overflow in parse_mpls at common/get.c:150. NOTE: this is different from CVE-2022-27942. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/736"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "820B7B7A-25F9-42C6-B0B0-0A2A34648477",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/appneta/tcpreplay/issues/736 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | You are opening a _bug report_ against the Tcpreplay project: we use
GitHub Issues for tracking bug reports and feature requests.
If you have a question about how to use Tcpreplay, you are at the wrong
site. You can ask a question on the [tcpreplay-users mailing list](https://sourceforge.net/p/tcpreplay/mailman/tc... | [Bug] heap-overflow in get.c:150 | https://api.github.com/repos/appneta/tcpreplay/issues/736/comments | 1 | 2022-07-24T14:40:26Z | 2022-08-07T03:03:15Z | https://github.com/appneta/tcpreplay/issues/736 | 1,315,924,974 | 736 |
CVE-2022-37768 | 2022-08-18T20:15:11.970 | libjpeg commit 281daa9 was discovered to contain an infinite loop via the component Frame::ParseTrailer. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/77"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:-:*:*:*:*:*:*:*",
"matchCriteriaId": "43E4B6B8-F045-4BF3-AC73-8F5596EA703C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": n... | https://github.com/thorfdbg/libjpeg/issues/77 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | version: latest commit 14bf94c
poc: [poc.zip](https://github.com/thorfdbg/libjpeg/files/9191143/poc.zip)
command: ./jpeg poc /dev/null
The backtrace in gdb:
```
(gdb) bt
#0 ByteStream::Get (this=0x790ae0) at bytestream.cpp:223
#1 0x000000000042331e in IOStream::PeekWord (this=0x790ae0)
at iostream.cpp:... | Infinite loop in Frame::ParseTrailer | https://api.github.com/repos/thorfdbg/libjpeg/issues/77/comments | 1 | 2022-07-26T15:59:16Z | 2022-08-03T12:22:36Z | https://github.com/thorfdbg/libjpeg/issues/77 | 1,318,449,876 | 77 |
CVE-2022-37769 | 2022-08-18T20:15:12.013 | libjpeg commit 281daa9 was discovered to contain a segmentation fault via HuffmanDecoder::Get at huffmandecoder.hpp. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/78"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:-:*:*:*:*:*:*:*",
"matchCriteriaId": "43E4B6B8-F045-4BF3-AC73-8F5596EA703C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": n... | https://github.com/thorfdbg/libjpeg/issues/78 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | Hi, there.
There is a segmentation fault in the newest master branch.
Here is the reproducing command:
`jpeg poc /dev/null`
```
Program received signal SIGSEGV, Segmentation fault.
HuffmanDecoder::Get (this=0x0, io=0x7933c8)
at /home/users/chluo/libjpeg/codestream/../coding/huffmandecoder.hpp:112
warn... | Segmentation fault in HuffmanDecoder::Get | https://api.github.com/repos/thorfdbg/libjpeg/issues/78/comments | 1 | 2022-07-27T04:04:02Z | 2022-08-03T12:23:15Z | https://github.com/thorfdbg/libjpeg/issues/78 | 1,318,990,797 | 78 |
CVE-2022-37770 | 2022-08-18T20:15:12.060 | libjpeg commit 281daa9 was discovered to contain a segmentation fault via LineMerger::GetNextLowpassLine at linemerger.cpp. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/79"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:-:*:*:*:*:*:*:*",
"matchCriteriaId": "43E4B6B8-F045-4BF3-AC73-8F5596EA703C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": n... | https://github.com/thorfdbg/libjpeg/issues/79 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | Hi, there.
There is a segmentation fault in the newest master branch.
Here is the reproducing command:
`jpeg poc /dev/null`
```
(gdb) bt
#0 0x00007ffff7f31270 in ?? () from /lib/x86_64-linux-gnu/libc.so.6
#1 0x0000000000711b6f in LineMerger::GetNextLowpassLine (this=0x85ed20, comp=2 '\002')
at linem... | Segmentation fault in LineMerger::GetNextLowpassLine | https://api.github.com/repos/thorfdbg/libjpeg/issues/79/comments | 3 | 2022-07-28T04:17:56Z | 2022-08-03T12:22:57Z | https://github.com/thorfdbg/libjpeg/issues/79 | 1,320,369,822 | 79 |
CVE-2022-36225 | 2022-08-19T17:15:07.897 | EyouCMS V1.5.8-UTF8-SP1 is vulnerable to Cross Site Request Forgery (CSRF) via the background, column management function and add. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/26"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.5.8:*:*:*:*:*:*:*",
"matchCriteriaId": "82E421EB-ECC8-42A4-8384-4187474D1AC3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | https://github.com/weng-xianhu/eyoucms/issues/26 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | version:V1.5.8-UTF8-SP1

In the background, column management function and add.
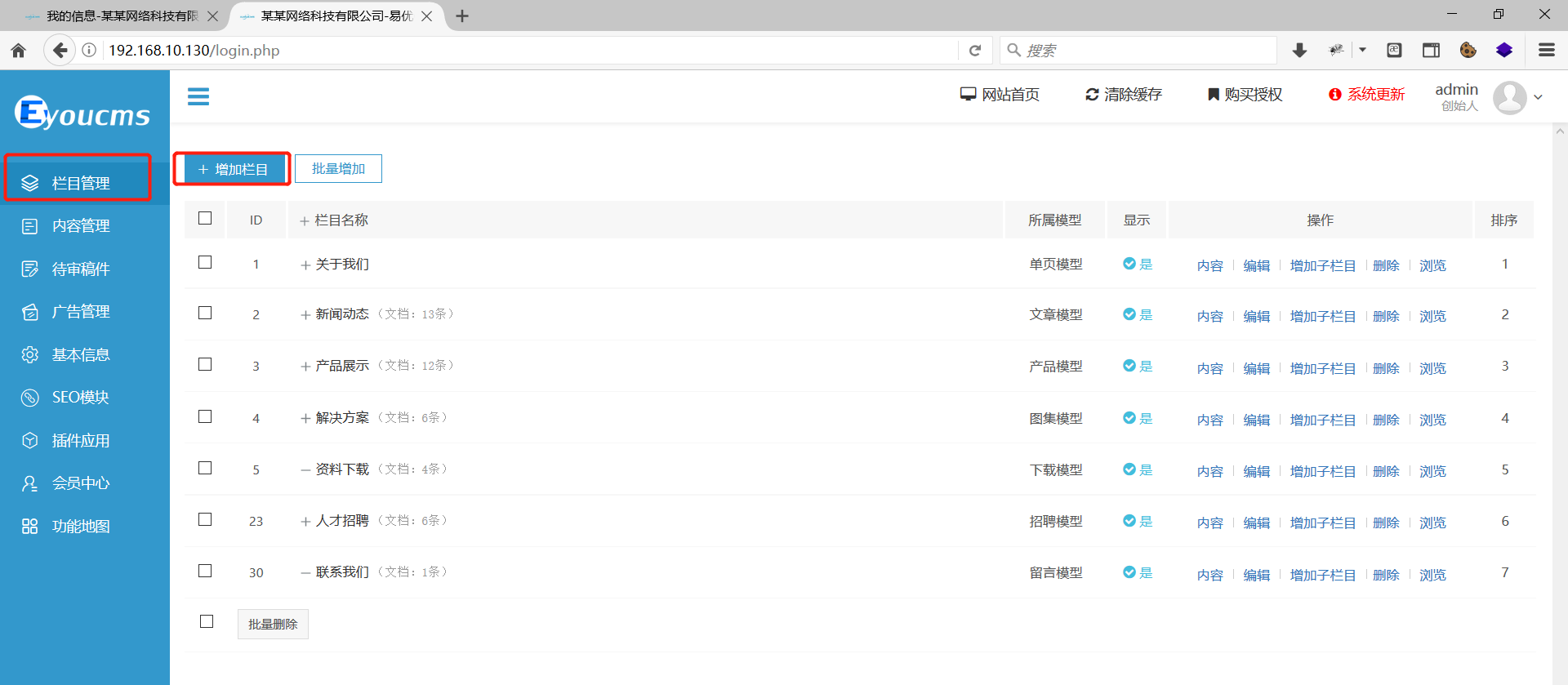
Add test data... | EyouCMS v1.5.8 has a vulnerability, Cross-site request forgery(CSRF) | https://api.github.com/repos/weng-xianhu/eyoucms/issues/26/comments | 2 | 2022-07-17T13:08:03Z | 2023-02-28T08:54:23Z | https://github.com/weng-xianhu/eyoucms/issues/26 | 1,307,093,003 | 26 |
CVE-2020-27793 | 2022-08-19T23:15:08.367 | An off-by-one overflow flaw was found in radare2 due to mismatched array length in core_java.c. This could allow an attacker to cause a crash, and perform a denail of service attack. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/radareorg/radare2/commit/ced0223c7a1b3b5344af315715cd28fe7c0d9ebc"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:radare:radare2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EEE8DA49-FB7A-4416-8942-56DD67E62CD9",
"versionEndExcluding": "4.4.0",
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/radareorg/radare2/issues/16304 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"radareorg",
"radare2"
] | ### Work environment
| Questions | Answers
|------------------------------------------------------|--------------------
| OS/arch/bits (mandatory) | Ubuntu x86 64
| File format of the file you reverse (mandatory) | ELF
| Architecture/bit... | unmatched array length in core_java.c | https://api.github.com/repos/radareorg/radare2/issues/16304/comments | 1 | 2020-03-25T04:35:41Z | 2020-03-26T11:02:44Z | https://github.com/radareorg/radare2/issues/16304 | 587,435,992 | 16,304 |
CVE-2020-27794 | 2022-08-19T23:15:08.427 | A double free issue was discovered in radare2 in cmd_info.c:cmd_info(). Successful exploitation could lead to modification of unexpected memory locations and potentially causing a crash. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.1,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "NONE",
"in... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/radareorg/radare2/commit/cb8b683758edddae2d2f62e8e63a738c39f92683"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:radare:radare2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EEE8DA49-FB7A-4416-8942-56DD67E62CD9",
"versionEndExcluding": "4.4.0",
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/radareorg/radare2/issues/16303 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"radareorg",
"radare2"
] | ### Work environment
| Questions | Answers
|------------------------------------------------------|--------------------
| OS/arch/bits (mandatory) | Ubuntu x86 64
| File format of the file you reverse (mandatory) | ELF
| Architecture/bit... | invalid free in cmd_info.c:cmd_info() | https://api.github.com/repos/radareorg/radare2/issues/16303/comments | 1 | 2020-03-25T04:31:50Z | 2020-03-26T11:28:51Z | https://github.com/radareorg/radare2/issues/16303 | 587,434,855 | 16,303 |
CVE-2020-27795 | 2022-08-19T23:15:08.487 | A segmentation fault was discovered in radare2 with adf command. In libr/core/cmd_anal.c, when command "adf" has no or wrong argument, anal_fcn_data (core, input + 1) --> RAnalFunction *fcn = r_anal_get_fcn_in (core->anal, core->offset, -1); returns null pointer for fcn causing segmentation fault later in ensure_fcn_ra... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/radareorg/radare2/commit/4d3811681a80f92a53e795f6a64c4b0fc2c8dd22"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:radare:radare2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EEE8DA49-FB7A-4416-8942-56DD67E62CD9",
"versionEndExcluding": "4.4.0",
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/radareorg/radare2/issues/16215 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"radareorg",
"radare2"
] | ### Work environment
| Questions | Answers
|------------------------------------------------------|--------------------
| OS/arch/bits (mandatory) | Ubuntu x86 64
| File format of the file you reverse (mandatory) | ELF
| Architecture/bit... | command "adf" Segmentation fault | https://api.github.com/repos/radareorg/radare2/issues/16215/comments | 1 | 2020-03-14T07:54:59Z | 2020-03-16T16:03:23Z | https://github.com/radareorg/radare2/issues/16215 | 581,094,359 | 16,215 |
CVE-2022-37199 | 2022-08-23T13:15:08.520 | JFinal CMS 5.1.0 is vulnerable to SQL Injection via /jfinal_cms/system/user/list. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jflyfox/jfinal_cms/issues/48"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jflyfox:jfinal_cms:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9B33E946-BD15-449C-B736-013773A64DF6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/jflyfox/jfinal_cms/issues/48 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jflyfox",
"jfinal_cms"
] | the route is /jfinal_cms/system/user/list


| There is a SQL injection vulnerability exists in JFinal CMS 5.1.0 again | https://api.github.com/repos/jflyfox/jfinal_cms/issues/49/comments | 0 | 2022-07-28T23:48:08Z | 2022-07-28T23:48:08Z | https://github.com/jflyfox/jfinal_cms/issues/49 | 1,321,600,614 | 49 |
CVE-2022-36527 | 2022-08-25T19:15:08.483 | Jfinal CMS v5.1.0 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the post title text field under the publish blog module. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jflyfox/jfinal_cms/issues/45"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jflyfox:jfinal_cms:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9B33E946-BD15-449C-B736-013773A64DF6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/jflyfox/jfinal_cms/issues/45 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jflyfox",
"jfinal_cms"
] | There is a stored XSS vulnerability in JFinal_cms 's publish blog module. An attacker could insert malicious XSS code into the post title. When users and administrators view the blog post, the malicious XSS code is triggered successfully.
First register a user to test it, then go to the submit blog post page and ins... | XSS vulnerability1 in jfinal_cms 5.1.0 | https://api.github.com/repos/jflyfox/jfinal_cms/issues/45/comments | 0 | 2022-07-18T04:43:11Z | 2022-07-18T04:43:11Z | https://github.com/jflyfox/jfinal_cms/issues/45 | 1,307,399,442 | 45 |
CVE-2020-27796 | 2022-08-25T20:15:08.487 | A heap-based buffer over-read was discovered in the invert_pt_dynamic function in p_lx_elf.cpp in UPX 4.0.0 via a crafted Mach-O file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/issues/392"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D3527302-7874-4400-B123-99C1CA6FE8EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | https://github.com/upx/upx/issues/392 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | Author: giantbranch of NSFOCUS Security Team
## What's the problem (or question)?
A heap buffer overflow in the latest commit of the devel branch
ASAN reports:
```
==21202==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x62f00000c530 at pc 0x00000058b076 bp 0x7ffdc9ecf670 sp 0x7ffdc9ecf668
READ of... | Heap buffer overflow in PackLinuxElf32::invert_pt_dynamic | https://api.github.com/repos/upx/upx/issues/392/comments | 1 | 2020-07-23T08:29:53Z | 2020-08-06T06:29:46Z | https://github.com/upx/upx/issues/392 | 664,292,638 | 392 |
CVE-2020-27797 | 2022-08-25T20:15:08.537 | An invalid memory address reference was discovered in the elf_lookup function in p_lx_elf.cpp in UPX 4.0.0 via a crafted Mach-O file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/issues/390"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D3527302-7874-4400-B123-99C1CA6FE8EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | https://github.com/upx/upx/issues/390 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | Author: giantbranch of NSFOCUS Security Team
## What's the problem (or question)?
Segmentation fault in PackLinuxElf32::elf_lookup(char const*) of /src/p_lx_elf.cpp in the latest commit of the devel branch
code link : [p_lx_elf.cpp#L5486](https://github.com/upx/upx/blob/87b73e5cfdc12da94c251b2cd83bb01c7d9f616... | Segmentation fault in PackLinuxElf32::elf_lookup(char const*) of /src/p_lx_elf.cpp | https://api.github.com/repos/upx/upx/issues/390/comments | 2 | 2020-07-23T08:06:10Z | 2020-08-06T06:28:39Z | https://github.com/upx/upx/issues/390 | 664,279,490 | 390 |
CVE-2020-27798 | 2022-08-25T20:15:08.583 | An invalid memory address reference was discovered in the adjABS function in p_lx_elf.cpp in UPX 4.0.0 via a crafted Mach-O file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/issues/396"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D3527302-7874-4400-B123-99C1CA6FE8EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | https://github.com/upx/upx/issues/396 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | Author: giantbranch of NSFOCUS Security Team
## What's the problem (or question)?
Segmentation fault in PackLinuxElf64::adjABS of p_lx_elf.cpp in the latest commit of the devel branch
code:
```
────────────────────────────────────────────────────────────────────────────────[ REGISTERS ]──────────────────────... | Segmentation fault in PackLinuxElf64::adjABS of p_lx_elf.cpp | https://api.github.com/repos/upx/upx/issues/396/comments | 1 | 2020-07-24T09:28:47Z | 2020-08-06T06:30:09Z | https://github.com/upx/upx/issues/396 | 665,044,143 | 396 |
CVE-2020-27799 | 2022-08-25T20:15:08.630 | A heap-based buffer over-read was discovered in the acc_ua_get_be32 function in miniacc.h in UPX 4.0.0 via a crafted Mach-O file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/issues/391"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D3527302-7874-4400-B123-99C1CA6FE8EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | https://github.com/upx/upx/issues/391 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | Author: giantbranch of NSFOCUS Security Team
## What's the problem (or question)?
A heap buffer overflow read in the latest commit of the devel branch
ASAN reports:
```
==21053==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x6160000014bb at pc 0x000000755961 bp 0x7ffe38d0c080 sp 0x7ffe38d0c078
... | Heap buffer overflow in acc_ua_get_be32() | https://api.github.com/repos/upx/upx/issues/391/comments | 1 | 2020-07-23T08:13:04Z | 2020-08-06T06:29:39Z | https://github.com/upx/upx/issues/391 | 664,283,181 | 391 |
CVE-2020-27800 | 2022-08-25T20:15:08.677 | A heap-based buffer over-read was discovered in the get_le32 function in bele.h in UPX 4.0.0 via a crafted Mach-O file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/issues/395"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D3527302-7874-4400-B123-99C1CA6FE8EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | https://github.com/upx/upx/issues/395 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | Author: giantbranch of NSFOCUS Security Team
## What's the problem (or question)?
A heap buffer overflow read in the latest commit of the devel branch
ASAN reports:
```
==5614==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x624000007da0 at pc 0x000000757233 bp 0x7ffe125eb8e0 sp 0x7ffe125eb8d8
REA... | Another heap buffer overflow in get_le32() | https://api.github.com/repos/upx/upx/issues/395/comments | 1 | 2020-07-24T08:10:02Z | 2020-08-06T06:30:04Z | https://github.com/upx/upx/issues/395 | 664,994,296 | 395 |
CVE-2020-27801 | 2022-08-25T20:15:08.727 | A heap-based buffer over-read was discovered in the get_le64 function in bele.h in UPX 4.0.0 via a crafted Mach-O file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/issues/394"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D3527302-7874-4400-B123-99C1CA6FE8EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | https://github.com/upx/upx/issues/394 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | Author: giantbranch of NSFOCUS Security Team
## What's the problem (or question)?
A heap buffer overflow read in the latest commit of the devel branch
ASAN reports:
```
==4525==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x7fab6ae5cdd8 at pc 0x000000757297 bp 0x7fff2d255a60 sp 0x7fff2d255a58
REA... | Heap buffer overflow in get_le64() | https://api.github.com/repos/upx/upx/issues/394/comments | 1 | 2020-07-24T06:42:22Z | 2020-08-06T06:29:58Z | https://github.com/upx/upx/issues/394 | 664,953,164 | 394 |
CVE-2020-27802 | 2022-08-25T20:15:08.777 | An floating point exception was discovered in the elf_lookup function in p_lx_elf.cpp in UPX 4.0.0 via a crafted Mach-O file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/issues/393"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D3527302-7874-4400-B123-99C1CA6FE8EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | https://github.com/upx/upx/issues/393 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | Author: giantbranch of NSFOCUS Security Team
## What's the problem (or question)?
Floating point exception was found in PackLinuxElf32::elf_lookup of p_lx_elf.cpp (the latest commit of the devel branch)
through debugging,because of div 0
```
────────────────────────────────────────────────────────────[ DISA... | Floating point exception in PackLinuxElf32::elf_lookup | https://api.github.com/repos/upx/upx/issues/393/comments | 1 | 2020-07-23T09:02:02Z | 2020-08-06T06:29:52Z | https://github.com/upx/upx/issues/393 | 664,311,420 | 393 |
CVE-2022-36168 | 2022-08-26T00:15:09.237 | A directory traversal vulnerability was discovered in Wuzhicms 4.1.0. via /coreframe/app/attachment/admin/index.php: | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 2.7,
"baseSeverity": "LOW",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Cigar-Fasion/CVE/issues/1"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhicms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2B76E69A-B2F3-4359-A7C0-046CEE2FAEEB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/wuzhicms/wuzhicms/issues/202 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | A directory traversal vulnerability was discovered in WUZHI CMS 4.1.0.
Directory traversal allows authenticated remote attackers to list files in any directory.
Vulnerability in /coreframe/app/attachment/admin/index.php:
```
public function dir()
{
$dir = isset($GLOBALS['dir']) && trim($GLOBALS['d... | Wuzhicms v4.1.0 /coreframe/app/attachment/admin/index.php hava a directory traversal Vulnerability | https://api.github.com/repos/wuzhicms/wuzhicms/issues/202/comments | 1 | 2022-07-12T03:28:46Z | 2023-01-08T02:20:43Z | https://github.com/wuzhicms/wuzhicms/issues/202 | 1,301,485,949 | 202 |
CVE-2021-3574 | 2022-08-26T16:15:08.943 | A vulnerability was found in ImageMagick-7.0.11-5, where executing a crafted file with the convert command, ASAN detects memory leaks. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "LOW",
"baseScore": 3.3,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integrityI... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ImageMagick/ImageMagick/commit/c6ad94fbb7b280f39c2fbbdc1c140e51b1b466e9"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.11-5:*:*:*:*:*:*:*",
"matchCriteriaId": "3769F997-3EBC-4222-B3D4-8709A7AA49FE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | https://github.com/ImageMagick/ImageMagick/issues/3540 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
I have written a descriptive issue title
I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to ensure it has not already been reported
I have verified that I am using the latest ... | AddressSanitizer report LeakSanitizer: detected memory leaks when executing convert command | https://api.github.com/repos/ImageMagick/ImageMagick/issues/3540/comments | 11 | 2021-04-13T14:50:19Z | 2022-11-30T17:19:10Z | https://github.com/ImageMagick/ImageMagick/issues/3540 | 857,040,605 | 3,540 |
CVE-2022-0284 | 2022-08-29T15:15:09.183 | A heap-based-buffer-over-read flaw was found in ImageMagick's GetPixelAlpha() function of 'pixel-accessor.h'. This vulnerability is triggered when an attacker passes a specially crafted Tagged Image File Format (TIFF) image to convert it into a PICON file format. This issue can potentially lead to a denial of service a... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2022-0284"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "90A073A6-900F-44EE-B29F-05CB65058078",
"versionEndExcluding": "7.1.0-20",
"versionEndIncluding": null,
"versionS... | https://github.com/ImageMagick/ImageMagick/issues/4729 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### ImageMagick version
7.1.0-20
### Operating system
Linux
### Operating system, version and so on
Linux ubuntu 5.4.0-73-generic #82~18.04.1-Ubuntu SMP Fri Apr 16 15:10:02 UTC 2021 x86_64 x86_64 x86_64 GNU/Linux
### Description
Hi, ImageMagick security team
This is ZhangJiaxing (@r0fm1a) from Codesafe Team of ... | Heap Buffer Overflow | https://api.github.com/repos/ImageMagick/ImageMagick/issues/4729/comments | 4 | 2022-01-19T07:07:49Z | 2022-02-19T13:35:53Z | https://github.com/ImageMagick/ImageMagick/issues/4729 | 1,107,736,894 | 4,729 |
CVE-2022-1115 | 2022-08-29T15:15:10.297 | A heap-buffer-overflow flaw was found in ImageMagick’s PushShortPixel() function of quantum-private.h file. This vulnerability is triggered when an attacker passes a specially crafted TIFF image file to ImageMagick for conversion, potentially leading to a denial of service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2022-1115"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "62ED872E-70D8-4736-9876-F307A77839D4",
"versionEndExcluding": "6.9.12-44",
"versionEndIncluding": null,
"version... | https://github.com/ImageMagick/ImageMagick/issues/4974 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### ImageMagick version
7.1.0-28
### Operating system
Linux
### Operating system, version and so on
OS: Ubuntu 20.04.3 LTS
Version: ImageMagick 7.1.0-28 Q16-HDRI x86_64 2022-03-04 https://imagemagick.org
Copyright: (C) 1999 ImageMagick Studio LLC
License: https://imagemagick.org/script/license.php ... | heap-buffer-overflow in magick at quantum-private.h PushShortPixel | https://api.github.com/repos/ImageMagick/ImageMagick/issues/4974/comments | 1 | 2022-03-22T02:10:38Z | 2022-03-24T01:28:05Z | https://github.com/ImageMagick/ImageMagick/issues/4974 | 1,176,173,021 | 4,974 |
CVE-2022-38530 | 2022-09-06T23:15:09.010 | GPAC v2.1-DEV-rev232-gfcaa01ebb-master was discovered to contain a stack overflow when processing ISOM_IOD. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2216"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | https://github.com/gpac/gpac/issues/2216 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | **version info:**
```
root:# MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev232-gfcaa01ebb-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your research:
GPAC Filters: https://doi.org/10.1145/3339825.3394929
GPAC: https://doi.org/10.114... | AddressSanitizer: stack-overflow when processing ISOM_IOD | https://api.github.com/repos/gpac/gpac/issues/2216/comments | 0 | 2022-07-02T17:45:58Z | 2022-07-12T17:13:10Z | https://github.com/gpac/gpac/issues/2216 | 1,292,105,535 | 2,216 |
CVE-2022-38272 | 2022-09-09T14:15:08.777 | JFinal CMS 5.1.0 is vulnerable to SQL Injection via /admin/article/list. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/jflyfox/jfinal_cms/issues/51"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jflyfox:jfinal_cms:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9B33E946-BD15-449C-B736-013773A64DF6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/jflyfox/jfinal_cms/issues/51 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"jflyfox",
"jfinal_cms"
] | Administrator login is required. The default account password is admin:admin123
## admin/article/list
There is a SQLI vul in background mode.The route is as following

vulnerable argument passing is as following
![ima... | Some SQL injection vulnerabilities exists in JFinal CMS 5.1.0 | https://api.github.com/repos/jflyfox/jfinal_cms/issues/51/comments | 0 | 2022-08-09T09:43:40Z | 2022-08-09T09:46:05Z | https://github.com/jflyfox/jfinal_cms/issues/51 | 1,332,993,619 | 51 |
CVE-2022-38282 | 2022-09-09T14:15:09.267 | JFinal CMS 5.1.0 is vulnerable to SQL Injection via /admin/videoalbum/list. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/jflyfox/jfinal_cms/issues/52"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jflyfox:jfinal_cms:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9B33E946-BD15-449C-B736-013773A64DF6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/jflyfox/jfinal_cms/issues/52 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"jflyfox",
"jfinal_cms"
] | Administrator login is required. The default account password is admin:admin123
## admin/videoalbum/list
There is a SQLI vul in background mode.The route is as following
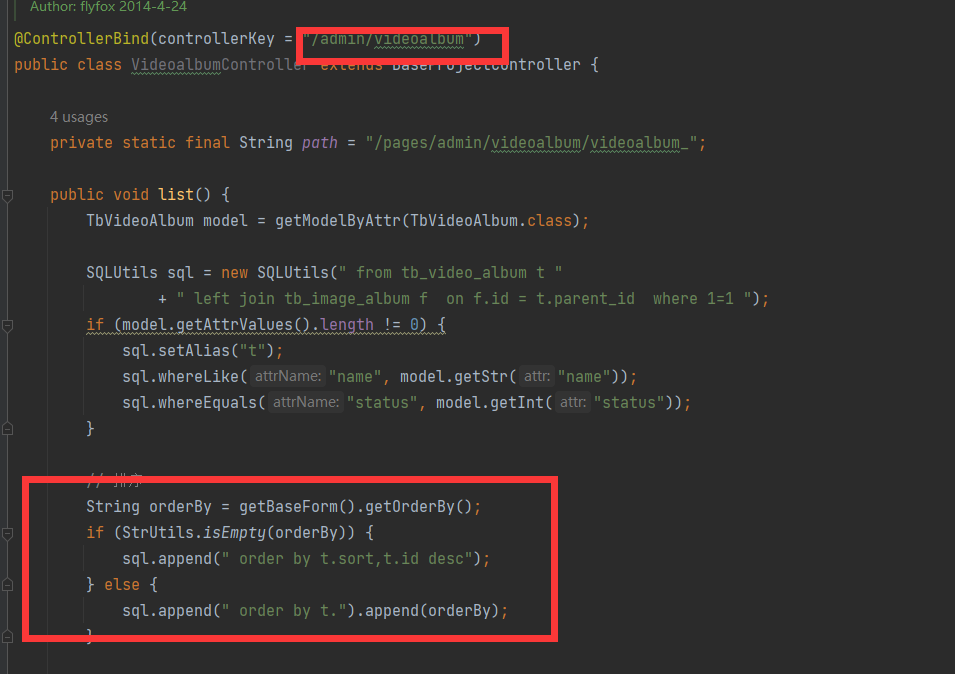
vulnerable argument passing is as following
![ima... | Some SQL injection vulnerabilities exists in JFinal CMS 5.1.0 | https://api.github.com/repos/jflyfox/jfinal_cms/issues/52/comments | 0 | 2022-08-09T10:01:49Z | 2022-08-09T10:01:49Z | https://github.com/jflyfox/jfinal_cms/issues/52 | 1,333,015,169 | 52 |
CVE-2022-38295 | 2022-09-12T21:15:11.243 | Cuppa CMS v1.0 was discovered to contain a cross-site scripting vulnerability at /table_manager/view/cu_user_groups. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Name field under the Add New Group function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/CuppaCMS/CuppaCMS/issues/34"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cuppacms:cuppacms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "983E1279-93C7-47D9-9AC8-EFB6D57B92E7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | https://github.com/CuppaCMS/CuppaCMS/issues/34 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"CuppaCMS",
"CuppaCMS"
] | Cross-Site Scripting exists in Cuppa CMS in Users tap.
Discoverer : **Team Am0namiss**(Members : [hoseongJ](https://github.com/hoseongJ), [studdcat](https://github.com/studdcat), [AnonyMousStu](https://github.com/AnonyMousStu), [GuJiseung](https://github.com/GuJiseung), [4dministrat0r](https://github.com/4dministrat0r... | XSS Vulnerability exists in Cuppa CMS in Users | https://api.github.com/repos/CuppaCMS/CuppaCMS/issues/34/comments | 0 | 2022-08-09T12:30:41Z | 2022-09-13T11:02:46Z | https://github.com/CuppaCMS/CuppaCMS/issues/34 | 1,333,188,097 | 34 |
CVE-2022-38296 | 2022-09-12T21:15:11.297 | Cuppa CMS v1.0 was discovered to contain an arbitrary file upload vulnerability via the File Manager. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/CuppaCMS/CuppaCMS/issues/33"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cuppacms:cuppacms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "983E1279-93C7-47D9-9AC8-EFB6D57B92E7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | https://github.com/CuppaCMS/CuppaCMS/issues/33 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"CuppaCMS",
"CuppaCMS"
] | File upload vulnerability exists in Cuppa CMS in File Manager tap.
Discoverer : **Team Am0namiss**(Members : [hoseongJ](https://github.com/hoseongJ), [studdcat](https://github.com/studdcat), [AnonyMousStu](https://github.com/AnonyMousStu), [GuJiseung](https://github.com/GuJiseung), [4dministrat0r](https://github.com/4... | File Upload Vulnerability exists in Cuppa CMS in File Manager | https://api.github.com/repos/CuppaCMS/CuppaCMS/issues/33/comments | 0 | 2022-08-09T12:17:02Z | 2022-09-13T11:02:31Z | https://github.com/CuppaCMS/CuppaCMS/issues/33 | 1,333,171,744 | 33 |
CVE-2022-37190 | 2022-09-13T23:15:08.620 | CuppaCMS 1.0 is vulnerable to Remote Code Execution (RCE). An authenticated user can control both parameters (action and function) from "/api/index.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/CuppaCMS/CuppaCMS/issues/22"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cuppacms:cuppacms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "983E1279-93C7-47D9-9AC8-EFB6D57B92E7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | https://github.com/CuppaCMS/CuppaCMS/issues/22 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"CuppaCMS",
"CuppaCMS"
] | An authenticated user can control both parameters (**action** and **function**) from **"/cuppa/api/index.php"**.


Reference: https://github.com/badru8612/Cuppa... | Authenticated Local File Inclusion vulnerability in cuppa api. | https://api.github.com/repos/CuppaCMS/CuppaCMS/issues/20/comments | 0 | 2022-01-24T07:59:02Z | 2022-01-25T23:08:06Z | https://github.com/CuppaCMS/CuppaCMS/issues/20 | 1,112,291,001 | 20 |
CVE-2022-40438 | 2022-09-14T21:15:10.627 | Buffer overflow vulnerability in function AP4_MemoryByteStream::WritePartial in mp42aac in Bento4 v1.6.0-639, allows attackers to cause a denial of service via a crafted file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/751"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/axiomatic-systems/Bento4/issues/751 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, developers of Bento4:
In the test of the binary mp42aac instrumented with ASAN. There are some inputs causing heap-buffer-overflow. Here is the ASAN mode output:
=================================================================
==4695==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x6190000027a0 at ... | Heap-buffer-overflow with ASAN in mp42aac | https://api.github.com/repos/axiomatic-systems/Bento4/issues/751/comments | 0 | 2022-09-07T02:21:29Z | 2022-09-18T23:10:27Z | https://github.com/axiomatic-systems/Bento4/issues/751 | 1,364,000,633 | 751 |
CVE-2022-40439 | 2022-09-14T21:15:10.670 | An memory leak issue was discovered in AP4_StdcFileByteStream::Create in mp42ts in Bento4 v1.6.0-639, allows attackers to cause a denial of service via a crafted file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/750"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/axiomatic-systems/Bento4/issues/750 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, developers of Bento4:
In the test of the binary mp42ts instrumented with ASAN. There are some inputs causing memory leaks. Here is the ASAN mode output:
=================================================================
==18321==ERROR: LeakSanitizer: detected memory leaks
Direct leak of 48 byte(s) in 1 objec... | Memory leaks with ASAN in mp42ts | https://api.github.com/repos/axiomatic-systems/Bento4/issues/750/comments | 0 | 2022-09-06T14:00:13Z | 2023-05-29T02:53:17Z | https://github.com/axiomatic-systems/Bento4/issues/750 | 1,363,336,565 | 750 |
CVE-2022-40736 | 2022-09-15T04:15:24.510 | An issue was discovered in Bento4 1.6.0-639. There ie excessive memory consumption in AP4_CttsAtom::Create in Core/Ap4CttsAtom.cpp. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/755"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/axiomatic-systems/Bento4/issues/755 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # summary
Hello, I use my fuzzer to fuzz binary mp4tag mp4split and mp42hevc, the three binary all crashede, and shows that allocator is out of memory trying to allocate 0xxxxxxx bytes. The version of Bento4 is the latest and the operation system is Ubuntu 18.04(docker). The following is the details.
# Bug1
```
... | Out of memory in AP4_CttsAtom::Create(unsigned int, AP4_ByteStream&) | https://api.github.com/repos/axiomatic-systems/Bento4/issues/755/comments | 2 | 2022-09-14T08:47:21Z | 2023-06-26T06:39:50Z | https://github.com/axiomatic-systems/Bento4/issues/755 | 1,372,600,841 | 755 |
CVE-2022-40737 | 2022-09-15T04:15:24.610 | An issue was discovered in Bento4 through 1.6.0-639. A buffer over-read exists in the function AP4_StdcFileByteStream::WritePartial located in System/StdC/Ap4StdCFileByteStream.cpp, called from AP4_ByteStream::Write and AP4_HdlrAtom::WriteFields. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/756"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "180AEBD6-AF89-4F0F-856E-D8B977C762C0",
"versionEndExcluding": null,
"versionEndIncluding": "1.6.0-639",
"versionStartExcl... | https://github.com/axiomatic-systems/Bento4/issues/756 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hello, I use fuzzer to test bianry mp4split, and found some vulnerabilities,the following is the details.
# Bug1
```
root@c511e4bf49bc:/mp4split/mp4split# ./mp4split FishFuzz/crashes/id:000000,sig:06,src:000011,op:flip1,pos:31240,1216870
=================================================================
==258946... | there are some vulnerabilities in binary mp4split | https://api.github.com/repos/axiomatic-systems/Bento4/issues/756/comments | 2 | 2022-09-14T11:20:27Z | 2023-06-26T06:40:26Z | https://github.com/axiomatic-systems/Bento4/issues/756 | 1,372,814,057 | 756 |
CVE-2022-38890 | 2022-09-15T16:15:10.687 | Nginx NJS v0.7.7 was discovered to contain a segmentation violation via njs_utf8_next at src/njs_utf8.h | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/569"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.7:*:*:*:*:*:*:*",
"matchCriteriaId": "B99556AB-3BAC-4553-8CDC-17292CF06AA8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nul... | https://github.com/nginx/njs/issues/569 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"nginx",
"njs"
] | the call stack is different with https://github.com/nginx/njs/issues/522
```
Environment
commit: 569292e0a74f2b1ec09566f3329f82bdd0d58e87
version: 0.7.7
Build :
./configure --cc=clang --address-sanitizer=YES
make
```
Poc
```js
function placeholder(){}
function main() {
var v2 = String... | Another way to trigger SEGV in njs_utf8_next cause oob read | https://api.github.com/repos/nginx/njs/issues/569/comments | 2 | 2022-08-25T02:58:03Z | 2022-09-02T00:51:09Z | https://github.com/nginx/njs/issues/569 | 1,350,249,226 | 569 |
CVE-2022-40774 | 2022-09-18T19:15:09.277 | An issue was discovered in Bento4 through 1.6.0-639. There is a NULL pointer dereference in AP4_StszAtom::GetSampleSize. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/757"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "180AEBD6-AF89-4F0F-856E-D8B977C762C0",
"versionEndExcluding": null,
"versionEndIncluding": "1.6.0-639",
"versionStartExcl... | https://github.com/axiomatic-systems/Bento4/issues/757 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi There,
I tested the binary mp42ts with my fuzzer, and a crash incurred, i.e., SEGV on an unknown address error. Here are the details:
```
AddressSanitizer:DEADLYSIGNAL
=================================================================
==6287==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x... | SEGV at AP4_StszAtom::GetSampleSize(unsigned int, unsigned int&) in binary mp42ts | https://api.github.com/repos/axiomatic-systems/Bento4/issues/757/comments | 2 | 2022-09-17T03:04:47Z | 2023-06-26T09:40:27Z | https://github.com/axiomatic-systems/Bento4/issues/757 | 1,376,646,543 | 757 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.