cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2023-49465 | 2023-12-07T20:15:38.370 | Libde265 v1.0.14 was discovered to contain a heap-buffer-overflow vulnerability in the derive_spatial_luma_vector_prediction function at motion.cc. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/strukturag/libde265/issues/435"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.debian.org/debian-lts-announce/2023/12/msg00022.html"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.14:*:*:*:*:*:*:*",
"matchCriteriaId": "B160149E-E072-4FC7-8E38-E3C469C78472",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/strukturag/libde265/issues/435 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"strukturag",
"libde265"
] | ### Description
heap-buffer-overflow `libde265/libde265/motion.cc:1860` in `derive_spatial_luma_vector_prediction(base_context*, de265_image*, slice_segment_header const*, int, int, int, int, int, int, int, int, int, int, unsigned char*, MotionVector*)`
### Version
```
dec265 v1.0.14
-----------------
usa... | heap-buffer-overflow `libde265/libde265/motion.cc:1860` in `derive_spatial_luma_vector_prediction` | https://api.github.com/repos/strukturag/libde265/issues/435/comments | 3 | 2023-11-23T02:44:12Z | 2023-12-20T10:49:09Z | https://github.com/strukturag/libde265/issues/435 | 2,007,396,948 | 435 | 5,794 |
CVE-2023-49467 | 2023-12-07T20:15:38.427 | Libde265 v1.0.14 was discovered to contain a heap-buffer-overflow vulnerability in the derive_combined_bipredictive_merging_candidates function at motion.cc. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/strukturag/libde265/issues/434"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.debian.org/debian-lts-announce/2023/12/msg00022.html"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.14:*:*:*:*:*:*:*",
"matchCriteriaId": "B160149E-E072-4FC7-8E38-E3C469C78472",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/strukturag/libde265/issues/434 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"strukturag",
"libde265"
] | ### Description
heap-buffer-overflow `eva/put/libde265/libde265/motion.cc:1443` in `derive_combined_bipredictive_merging_candidates(base_context const*, slice_segment_header const*, PBMotion*, int*, int)`
### Version
```
dec265 v1.0.14
-----------------
usage: dec265 [options] videofile.bin
The video fil... | heap-buffer-overflow `libde265/libde265/motion.cc:1443` in `derive_combined_bipredictive_merging_candidates` | https://api.github.com/repos/strukturag/libde265/issues/434/comments | 3 | 2023-11-23T02:39:56Z | 2023-12-20T10:47:44Z | https://github.com/strukturag/libde265/issues/434 | 2,007,393,613 | 434 | 5,795 |
CVE-2023-49468 | 2023-12-07T20:15:38.477 | Libde265 v1.0.14 was discovered to contain a global buffer overflow vulnerability in the read_coding_unit function at slice.cc. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/strukturag/libde265/issues/432"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.debian.org/debian-lts-announce/2023/12/msg00022.html"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.14:*:*:*:*:*:*:*",
"matchCriteriaId": "B160149E-E072-4FC7-8E38-E3C469C78472",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/strukturag/libde265/issues/432 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"strukturag",
"libde265"
] | ### Description
global-buffer-overflow `libde265/libde265/slice.cc:4493` in `read_coding_unit(thread_context*, int, int, int, int)`
### Version
```
dec265 v1.0.14
-----------------
usage: dec265 [options] videofile.bin
The video file must be a raw bitstream, or a stream with NAL units (option -n).
opt... | global-buffer-overflow in read_coding_unit | https://api.github.com/repos/strukturag/libde265/issues/432/comments | 8 | 2023-11-22T10:12:42Z | 2023-12-20T19:14:23Z | https://github.com/strukturag/libde265/issues/432 | 2,005,999,851 | 432 | 5,796 |
CVE-2023-6507 | 2023-12-08T19:15:08.440 | An issue was found in CPython 3.12.0 `subprocess` module on POSIX platforms. The issue was fixed in CPython 3.12.1 and does not affect other stable releases.
When using the `extra_groups=` parameter with an empty list as a value (ie `extra_groups=[]`) the logic regressed to not call `setgroups(0, NULL)` before calling... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "ADJACENT_NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
... | [
{
"source": "cna@python.org",
"tags": null,
"url": "https://github.com/python/cpython/commit/10e9bb13b8dcaa414645b9bd10718d8f7179e82b"
},
{
"source": "cna@python.org",
"tags": null,
"url": "https://github.com/python/cpython/commit/85bbfa8a4bbdbb61a3a84fbd7cb29a4096ab8a06"
},
{
"s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:python:python:3.12.0:-:*:*:*:*:*:*",
"matchCriteriaId": "5C76EDC2-43FF-448B-B65C-20AC83D680FE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"269"
] | 269 | https://github.com/python/cpython/issues/112334 | [
"Issue Tracking",
"Patch"
] | github.com | [
"python",
"cpython"
] | # Bug report
### Bug description:
Apologies if this is a duplicate. I couldn’t find a similar report, though.
# The issue and how to reproduce
We’re seeing a performance regression since 124af17b6e. The best way to reproduce it is to spawn lots of processes from a `ThreadPoolExecutor`. For example:
```python
#!/us... | subprocess.Popen: Performance regression on Linux since 124af17b6e [CVE-2023-6507] | https://api.github.com/repos/python/cpython/issues/112334/comments | 3 | 2023-11-23T10:53:20Z | 2023-12-08T21:00:58Z | https://github.com/python/cpython/issues/112334 | 2,007,974,265 | 112,334 | 5,797 |
CVE-2023-46932 | 2023-12-09T07:15:07.663 | Heap Buffer Overflow vulnerability in GPAC version 2.3-DEV-rev617-g671976fcc-master, allows attackers to execute arbitrary code and cause a denial of service (DoS) via str2ulong class in src/media_tools/avilib.c in gpac/MP4Box. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/gpac/gpac/issues/2669"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/gpac/gpac/issues/2669"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev617-g671976fcc-master:*:*:*:*:*:*:*",
"matchCriteriaId": "F540C691-D615-4A9B-8DD6-69B8488E3BA1",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2669 | [
"Exploit"
] | github.com | [
"gpac",
"gpac"
] | # heap-buffer-overflow in str2ulong src/media_tools/avilib.c:137:16 in gpac/MP4Box
### Description
Heap-buffer-overflow in MP4Box.
#0 0x7ffff694c441 in str2ulong /afltest/gpac2/src/media_tools/avilib.c:137:16
### Version
```shell
MP4Box - GPAC version 2.3-DEV-rev617-g671976fcc-master
(c) 2000-2023 Teleco... | heap-buffer-overflow in str2ulong src/media_tools/avilib.c:137:16 in gpac/MP4Box | https://api.github.com/repos/gpac/gpac/issues/2669/comments | 0 | 2023-10-26T18:25:32Z | 2023-12-04T10:07:48Z | https://github.com/gpac/gpac/issues/2669 | 1,964,116,818 | 2,669 | 5,798 |
CVE-2022-48614 | 2023-12-10T19:15:07.410 | Special:Ask in Semantic MediaWiki before 4.0.2 allows Reflected XSS. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/SemanticMediaWiki/SemanticMediaWiki/issues/5262"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes"
],
"url": "https://www.semantic-mediawiki.org/wiki/Semantic_MediaWiki_4.0.2... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:semantic-mediawiki:semantic_mediawiki:*:*:*:*:*:mediawiki:*:*",
"matchCriteriaId": "DADF6CC5-2DF1-47D9-BC1B-33BAEDCF926F",
"versionEndExcluding": "4.0.2",
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/SemanticMediaWiki/SemanticMediaWiki/issues/5262 | [
"Issue Tracking"
] | github.com | [
"SemanticMediaWiki",
"SemanticMediaWiki"
] | ### Setup
- SMW version: 3.2.3
- MW version: 1.36.4
- PHP version: 7.4.28 (fpm-fcgi)
- DB system (MySQL, Blazegraph, etc.) and version: MySQL 5.7.12
### Issue
There is a possible "reflected XSS" vulnerability in Special:Ask. Given that it's a potential security risk to, let me know if there is a way I can s... | Possible Reflected XSS vulnerability in Special:Ask | https://api.github.com/repos/SemanticMediaWiki/SemanticMediaWiki/issues/5262/comments | 4 | 2022-06-10T21:39:13Z | 2022-07-12T15:48:51Z | https://github.com/SemanticMediaWiki/SemanticMediaWiki/issues/5262 | 1,268,046,033 | 5,262 | 5,799 |
CVE-2023-50463 | 2023-12-10T23:15:07.247 | The caddy-geo-ip (aka GeoIP) middleware through 0.6.0 for Caddy 2, when trust_header X-Forwarded-For is used, allows attackers to spoof their source IP address via an X-Forwarded-For header, which may bypass a protection mechanism (trusted_proxy directive in reverse_proxy or IP address range restrictions). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "https://caddyserver.com/v2"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/shift72/caddy-geo-ip/issues/4"
},
{
"source": "cve@mitre.org",
"tags"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:caddyserver:caddy:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E7FEAAE7-1B58-403B-A74C-3E7C3A1229E6",
"versionEndExcluding": null,
"versionEndIncluding": "0.6.0",
"versionStartExclu... | [
"290"
] | 290 | https://github.com/shift72/caddy-geo-ip/issues/4 | [
"Third Party Advisory"
] | github.com | [
"shift72",
"caddy-geo-ip"
] | When trust_header is configured, req.RemoteAddr is overwritten. This allows spoofing the remote address in following checks.
In the example the {remote_host} variable is changed.
```
geo_ip {
db_path /var/lib/GeoIP/GeoLite2-City.mmdb
trust_header X-Forwarded-For
}
respond /test 200 {
... | Security: trust_header overwrites req.RemoteAddr globally | https://api.github.com/repos/shift72/caddy-geo-ip/issues/4/comments | 0 | 2023-02-07T22:27:53Z | 2023-02-07T22:27:53Z | https://github.com/shift72/caddy-geo-ip/issues/4 | 1,575,120,425 | 4 | 5,800 |
CVE-2023-49488 | 2023-12-11T21:15:07.283 | A cross-site scripting (XSS) vulnerability in Openfiler ESA v2.99.1 allows attackers to execute arbitrary web scripts or HTML via injecting a crafted payload into the nic parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Hebing123/cve/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openfiler:openfiler:2.99.1:*:*:*:*:*:*:*",
"matchCriteriaId": "9E197DA0-C790-44F4-B91D-1BCB91BE47F1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"79"
] | 79 | https://github.com/Hebing123/cve/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Hebing123",
"cve"
] | https://[ip]:446/admin/system.html?nic=eth0%3CScRiPt%20%3Ealert(document.cookie)%3C/ScRiPt%3E&step=addvlan

| Openfiler ESA 2.99.1 Reflective XSS Vulnerability | https://api.github.com/repos/Hebing123/cve/issues/1/comments | 1 | 2023-11-23T03:00:09Z | 2024-01-11T03:30:06Z | https://github.com/Hebing123/cve/issues/1 | 2,007,406,882 | 1 | 5,801 |
CVE-2023-49494 | 2023-12-11T21:15:07.397 | DedeCMS v5.7.111 was discovered to contain a reflective cross-site scripting (XSS) vulnerability via the component select_media_post_wangEditor.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://dedecms.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Hebing123/cve/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364d... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dedecms:dedecms:5.7.111:*:*:*:*:*:*:*",
"matchCriteriaId": "377F392A-A04B-4E7A-BBE8-F77CE65BDFCF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/Hebing123/cve/issues/3 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Hebing123",
"cve"
] | **Description**
DedeCMS-V5.7.111 has Reflective XSS vulnerability in filename parameter of select_media_post_wangEditor.php
**Proof of Concept**
http://target-ip/uploads/include/dialog/select_media_post_wangEditor.php?filename=1%3Cinput%20onfocus=eval(atob(this.id))%20id=YWxlcnQoZG9jdW1lbnQuY29va2llKTs=%20autofo... | DedeCMS-V5.7.111 Reflective XSS vulnerability in select_media_post_wangEditor.php | https://api.github.com/repos/Hebing123/cve/issues/3/comments | 2 | 2023-11-23T10:22:21Z | 2024-11-21T10:33:32Z | https://github.com/Hebing123/cve/issues/3 | 2,007,897,963 | 3 | 5,802 |
CVE-2023-45292 | 2023-12-11T22:15:06.677 | When using the default implementation of Verify to check a Captcha, verification can be bypassed. For example, if the first parameter is a non-existent id, the second parameter is an empty string, and the third parameter is true, the function will always consider the Captcha to be correct. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "security@golang.org",
"tags": [
"Patch"
],
"url": "https://github.com/mojocn/base64Captcha/commit/5ab86bd6f333aad3936f912fc52b411168dcd4a7"
},
{
"source": "security@golang.org",
"tags": [
"Patch"
],
"url": "https://github.com/mojocn/base64Captcha/commit/9... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mojotv:base64captcha:*:*:*:*:*:go:*:*",
"matchCriteriaId": "20EF9A8D-B33C-468E-9928-2E80A0C1EA00",
"versionEndExcluding": "1.3.6",
"versionEndIncluding": null,
"versionStartE... | [
"345"
] | 345 | https://github.com/mojocn/base64Captcha/issues/120 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"mojocn",
"base64Captcha"
] | 当store.Verify的answer为空字符串并且id不存在时返回值永远为true
复原代码
``` go
package main
import (
"fmt"
"strconv"
"testing"
"github.com/mojocn/base64Captcha"
)
func TestCat(t *testing.T) {
var store = base64Captcha.DefaultMemStore
fmt.Println(strconv.FormatBool(store.Verify("dsad", "", true)))
}
```
| 特殊值永远成功漏洞 CVE-2023-45292 GO-2023-2386 | https://api.github.com/repos/mojocn/base64Captcha/issues/120/comments | 2 | 2023-12-01T11:40:40Z | 2023-12-08T12:48:54Z | https://github.com/mojocn/base64Captcha/issues/120 | 2,020,713,875 | 120 | 5,803 |
CVE-2023-49802 | 2023-12-11T22:15:06.730 | The LinkedCustomFields plugin for MantisBT allows users to link values between two custom fields, creating linked drop-downs. Prior to version 2.0.1, cross-site scripting in the MantisBT LinkedCustomFields plugin allows Javascript execution, when a crafted Custom Field is linked via the plugin and displayed when report... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 6.7,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"integ... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/mantisbt-plugins/LinkedCustomFields/commit/30e5ae751e40d7ae18bfd794fd48671477b3d286"
},
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Patch"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mantisbt:linked_custom_fields:*:*:*:*:*:mantisbt:*:*",
"matchCriteriaId": "0A8DBAA5-48FF-4744-A583-D7CA7A1DAFF1",
"versionEndExcluding": "2.0.1",
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/mantisbt-plugins/LinkedCustomFields/issues/10 | [
"Issue Tracking",
"Patch"
] | github.com | [
"mantisbt-plugins",
"LinkedCustomFields"
] | Problem: linked fields with special characters (like &) can't be saved
Solution: use htmlspecialchars_decode in LinkedCustomFields.API.php
static function getLinkedFieldId( $p_source_field_id ) {
$t_query = "SELECT target_field_id FROM " . plugin_table( 'data' ) . " WHERE custom_field_id = " . db_param();
... | CVE-2023-49802 : Problem with special characters | https://api.github.com/repos/mantisbt-plugins/LinkedCustomFields/issues/10/comments | 3 | 2023-08-10T10:06:07Z | 2023-12-13T13:19:06Z | https://github.com/mantisbt-plugins/LinkedCustomFields/issues/10 | 1,844,863,029 | 10 | 5,804 |
CVE-2023-49990 | 2023-12-12T14:15:07.553 | Espeak-ng 1.52-dev was discovered to contain a buffer-overflow via the function SetUpPhonemeTable at synthdata.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "LOW",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/espeak-ng/espeak-ng/issues/1824"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:espeak-ng:espeak-ng:1.52:dev:*:*:*:*:*:*",
"matchCriteriaId": "B073B0F6-3979-4E7D-BF6F-29C9EB1F3480",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"120"
] | 120 | https://github.com/espeak-ng/espeak-ng/issues/1824 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"espeak-ng",
"espeak-ng"
] | **System info**
Ubuntu x86_64, clang 12.0
version: espeak-ng(1.52-dev)
**Command line**
./espeak-ng -f poc -w /dev/null
**Poc**
poc:[poc](https://github.com/SEU-SSL/Poc/blob/main/espeak-ng/id_000064%2Csig_11%2Csrc_008778%2Cop_havoc%2Crep_2)
**AddressSanitizer output**
==4070074==ERROR: AddressSanitizer: g... | global-buffer-overflow exists in the function SetUpPhonemeTable in synthdata.c | https://api.github.com/repos/espeak-ng/espeak-ng/issues/1824/comments | 1 | 2023-11-13T03:26:19Z | 2023-12-17T12:53:26Z | https://github.com/espeak-ng/espeak-ng/issues/1824 | 1,989,818,650 | 1,824 | 5,805 |
CVE-2023-49991 | 2023-12-12T14:15:07.600 | Espeak-ng 1.52-dev was discovered to contain a Stack Buffer Underflow via the function CountVowelPosition at synthdata.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "LOW",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/espeak-ng/espeak-ng/issues/1825"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:espeak-ng:espeak-ng:1.52:dev:*:*:*:*:*:*",
"matchCriteriaId": "B073B0F6-3979-4E7D-BF6F-29C9EB1F3480",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"787"
] | 787 | https://github.com/espeak-ng/espeak-ng/issues/1825 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"espeak-ng",
"espeak-ng"
] | **System info**
Ubuntu x86_64, clang 12.0
version: espeak-ng(1.52-dev)
**Command line**
./espeak-ng -f poc -w /dev/null
**Poc**
poc:[poc](https://github.com/SEU-SSL/Poc/blob/main/espeak-ng/id_000092%2Csig_11%2Csrc_009714%2Cop_havoc%2Crep_2)
**AddressSanitizer output**
==4070186==ERROR: AddressSanitizer: s... | stack-buffer-underflow exists in the function CountVowelPosition in synthdata.c | https://api.github.com/repos/espeak-ng/espeak-ng/issues/1825/comments | 1 | 2023-11-13T03:33:30Z | 2023-12-17T12:53:16Z | https://github.com/espeak-ng/espeak-ng/issues/1825 | 1,989,824,628 | 1,825 | 5,806 |
CVE-2023-49992 | 2023-12-12T14:15:07.653 | Espeak-ng 1.52-dev was discovered to contain a Stack Buffer Overflow via the function RemoveEnding at dictionary.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "LOW",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/espeak-ng/espeak-ng/issues/1827"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:espeak-ng:espeak-ng:1.52:dev:*:*:*:*:*:*",
"matchCriteriaId": "B073B0F6-3979-4E7D-BF6F-29C9EB1F3480",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"787"
] | 787 | https://github.com/espeak-ng/espeak-ng/issues/1827 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"espeak-ng",
"espeak-ng"
] | **System info**
Ubuntu x86_64, clang 12.0
version: espeak-ng(1.52-dev)
**Command line**
./espeak-ng -f poc -w /dev/null
**Poc**
poc:[poc](https://github.com/SEU-SSL/Poc/blob/main/espeak-ng/id_000209%2Csig_07%2Csrc_000384%2Cop_havoc%2Crep_32)
**AddressSanitizer output**
==4070654==ERROR: AddressSanitizer: ... | stack-buffer-overflow exists in the function RemoveEnding in dictionary.c | https://api.github.com/repos/espeak-ng/espeak-ng/issues/1827/comments | 1 | 2023-11-13T03:37:25Z | 2023-12-17T12:53:03Z | https://github.com/espeak-ng/espeak-ng/issues/1827 | 1,989,827,779 | 1,827 | 5,807 |
CVE-2023-49993 | 2023-12-12T14:15:07.700 | Espeak-ng 1.52-dev was discovered to contain a Buffer Overflow via the function ReadClause at readclause.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "LOW",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/espeak-ng/espeak-ng/issues/1826"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:espeak-ng:espeak-ng:1.52:dev:*:*:*:*:*:*",
"matchCriteriaId": "B073B0F6-3979-4E7D-BF6F-29C9EB1F3480",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"120"
] | 120 | https://github.com/espeak-ng/espeak-ng/issues/1826 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"espeak-ng",
"espeak-ng"
] | **System info**
Ubuntu x86_64, clang 12.0
version: espeak-ng(1.52-dev)
**Command line**
./espeak-ng -f poc -w /dev/null
**Poc**
poc:[poc](https://github.com/SEU-SSL/Poc/blob/main/espeak-ng/id_000205%2Csig_11%2Csrc_013749%2Cop_havoc%2Crep_4)
**AddressSanitizer output**
==4070638==ERROR: AddressSanitizer: g... | global-buffer-overflow exists in the function ReadClause in readclause.c | https://api.github.com/repos/espeak-ng/espeak-ng/issues/1826/comments | 1 | 2023-11-13T03:35:17Z | 2023-12-17T12:53:10Z | https://github.com/espeak-ng/espeak-ng/issues/1826 | 1,989,826,100 | 1,826 | 5,808 |
CVE-2023-49994 | 2023-12-12T14:15:07.750 | Espeak-ng 1.52-dev was discovered to contain a Floating Point Exception via the function PeaksToHarmspect at wavegen.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/espeak-ng/espeak-ng/issues/1823"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:espeak-ng:espeak-ng:1.52:dev:*:*:*:*:*:*",
"matchCriteriaId": "B073B0F6-3979-4E7D-BF6F-29C9EB1F3480",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"697"
] | 697 | https://github.com/espeak-ng/espeak-ng/issues/1823 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"espeak-ng",
"espeak-ng"
] | **System info**
Ubuntu x86_64, clang 12.0
version: espeak-ng(1.52-dev)
**Command line**
./espeak-ng -f poc -w /dev/null
**Poc**
poc:[poc](https://github.com/SEU-SSL/Poc/blob/main/espeak-ng/id_000000%2Csig_08%2Csrc_003156%2B002428%2Cop_splice%2Crep_32)
**AddressSanitizer output**
==4069818==ERROR: AddressS... | Floating Point Exception exists in the function PeaksToHarmspect in wavegen.c | https://api.github.com/repos/espeak-ng/espeak-ng/issues/1823/comments | 1 | 2023-11-13T03:23:53Z | 2023-12-17T12:29:31Z | https://github.com/espeak-ng/espeak-ng/issues/1823 | 1,989,816,339 | 1,823 | 5,809 |
CVE-2023-6755 | 2023-12-13T13:15:09.203 | A vulnerability was found in DedeBIZ 6.2 and classified as critical. This issue affects some unknown processing of the file /src/admin/content_batchup_action.php. The manipulation of the argument endid leads to sql injection. The attack may be initiated remotely. The exploit has been disclosed to the public and may be ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "MULTIPLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PAR... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ycwxy/test/issues/1"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dedebiz:dedebiz:6.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4240B26E-641D-4E8C-8001-B86FA8388C57",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"89"
] | 89 | https://github.com/ycwxy/test/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ycwxy",
"test"
] | [Suggested description]
SQL injection vulnerability exists in DedeBIZ V6.2 in /src/admin/content_batchup_action.php
[Vulnerability Type]
SQL INJECTION
[Vendor of Product]
https://github.com/DedeBIZ/DedeV6
[Affected Product Code Base]
DedeBIZ V6.2
[Affected Component]
File: /src/admin/content_batchup_action.php... | SQL injection vulnerability exists in DedeBIZ V6.2 in /src/admin/content_batchup_action.php | https://api.github.com/repos/ycwxy/test/issues/1/comments | 0 | 2023-12-03T07:01:55Z | 2023-12-03T07:01:55Z | https://github.com/ycwxy/test/issues/1 | 2,022,398,500 | 1 | 5,810 |
CVE-2023-6772 | 2023-12-13T19:15:08.513 | A vulnerability, which was classified as critical, was found in OTCMS 7.01. Affected is an unknown function of the file /admin/ind_backstage.php. The manipulation of the argument sqlContent leads to sql injection. It is possible to launch the attack remotely. The exploit has been disclosed to the public and may be used... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "MULTIPLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PAR... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Num-Nine/CVE/issues/8"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory",
"VDB Entry"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:otcms:otcms:7.01:*:*:*:*:*:*:*",
"matchCriteriaId": "18E47DA7-DFAF-4D23-A3F5-3C1631975FA1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"89"
] | 89 | https://github.com/Num-Nine/CVE/issues/8 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Num-Nine",
"CVE"
] | 1.Official website:http://otcms.com/
2.Hole location: /admin/ind_backstage.php
3.Log in to the background and send the packet as follows
POST /admin/sysCheckFile_deal.php?mudi=sql HTTP/1.1
Host: otcms.com
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/118.0... | sql injection exists in otcmsV7.01 | https://api.github.com/repos/QianGeG/CVE/issues/8/comments | 0 | 2023-12-11T09:51:15Z | 2023-12-11T09:51:15Z | https://github.com/QianGeG/CVE/issues/8 | 2,035,266,663 | 8 | 5,811 |
CVE-2023-44709 | 2023-12-14T06:15:42.743 | PlutoSVG commit 336c02997277a1888e6ccbbbe674551a0582e5c4 and before was discovered to contain an integer overflow via the component plutosvg_load_from_memory. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/sunwithmoon/3f810c27d2e553f9d31bd7c50566f15b#file-cve-2023-44709"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sammycage:plutosvg:-:*:*:*:*:*:*:*",
"matchCriteriaId": "93DFAB49-4564-4F0C-8CFD-AF6696E7123C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"190"
] | 190 | https://github.com/sammycage/plutosvg/issues/7 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"sammycage",
"plutosvg"
] | # Summary
An integer overflow in the allocated size of `calloc` causes a segment fault.
It might lead to heap overflow and arbitrary code execution.
# Steps to reproduce
code:
```C
#include <plutosvg.h>
#include <stdlib.h>
#include <stdio.h>
int main(int argc, char* argv[])
{
plutovg_surface_t* surfa... | CWE-131 (Incorrect Calculation of Buffer Size) in plutosvg_load_from_memory | https://api.github.com/repos/sammycage/plutosvg/issues/7/comments | 4 | 2023-09-21T08:28:35Z | 2024-08-02T18:05:07Z | https://github.com/sammycage/plutosvg/issues/7 | 1,906,410,380 | 7 | 5,812 |
CVE-2023-50073 | 2023-12-14T15:15:10.260 | EmpireCMS v7.5 was discovered to contain a SQL injection vulnerability via the ftppassword parameter at SetEnews.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/leadscloud/EmpireCMS/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/leadscloud/EmpireCMS/issues/7"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:leadscloud:empirecms:7.5:*:*:*:*:*:*:*",
"matchCriteriaId": "A3A906A8-1B33-4B3F-887A-AE83BB918F9D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/leadscloud/EmpireCMS/issues/7 | [
"Exploit"
] | github.com | [
"leadscloud",
"EmpireCMS"
] | **Brief of this vulnerability**
EmpireCMS v7.5 has an SQL injection vulnerability when configuring FTP passwords
**Test Environment**
Windows10
PHP 5.4.45+Apache/2.4.39
**Affect version**
EmpireCMS 7.5
**Vulnerable Code**
e\admin\SetEnews.php line 353
 vulnerability in the component /logs/dopost.html in RPCMS v3.5.5 allows attackers to execute arbitrary web scripts or HTML via a crafted payload. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/ralap-z/rpcms/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/ralap-z/rpcms/issues/7"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rpcms:rpcms:3.5.5:*:*:*:*:*:*:*",
"matchCriteriaId": "60ED4BE1-FE0A-4C99-B93B-5F498B69F789",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/ralap-z/rpcms/issues/7 | [
"Exploit"
] | github.com | [
"ralap-z",
"rpcms"
] | 1、"设置"->"基本设置"->"统计代码":


2、"导航":
 vulnerability in EyouCMS-V1.6.5-UTF8-SP1 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Public Security Registration Number parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/56"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.5-utf8-sp1:*:*:*:*:*:*:*",
"matchCriteriaId": "920C4179-21B4-4BEC-AC3C-8C7530C41B13",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"79"
] | 79 | https://github.com/weng-xianhu/eyoucms/issues/56 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | Version : V1.6.5

Vulnerability point 1:
"基本信息"->"备案号"&“公安备案号”->"代码模式",HTML code can be edited directly:

![ima... | EyouCMS-V1.6.5-UTF8-SP1 has a stored XSS vulnerability | https://api.github.com/repos/weng-xianhu/eyoucms/issues/56/comments | 1 | 2023-12-08T08:39:23Z | 2024-03-22T06:31:10Z | https://github.com/weng-xianhu/eyoucms/issues/56 | 2,032,215,326 | 56 | 5,815 |
CVE-2023-6563 | 2023-12-14T18:15:45.540 | An unconstrained memory consumption vulnerability was discovered in Keycloak. It can be triggered in environments which have millions of offline tokens (> 500,000 users with each having at least 2 saved sessions). If an attacker creates two or more user sessions and then open the "consents" tab of the admin User Interf... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.7,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Vendor Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2023:7854"
},
{
"source": "secalert@redhat.com",
"tags": [
"Vendor Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2023:7855"
},
{
"sourc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redhat:keycloak:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DD663F41-3B6D-4AF0-9ABA-1F3BF292C632",
"versionEndExcluding": "21.0.0",
"versionEndIncluding": null,
"versionStartExclud... | [
"770"
] | 770 | https://github.com/keycloak/keycloak/issues/13340 | [
"Issue Tracking"
] | github.com | [
"keycloak",
"keycloak"
] | ### Describe the bug
We have approx. 6 million offline sessions in the database and enabled lazy loading of offline sessions.
We ran into performance issues:
If a user has >= 2 user sessions and you open the consents tab in the admin UI for this user, the following code tries to load the corresponding offline... | Performance Issues with many offline sessions | https://api.github.com/repos/keycloak/keycloak/issues/13340/comments | 8 | 2022-07-26T15:15:00Z | 2023-03-04T17:35:10Z | https://github.com/keycloak/keycloak/issues/13340 | 1,318,390,700 | 13,340 | 5,816 |
CVE-2023-50471 | 2023-12-14T20:15:53.130 | cJSON v1.7.16 was discovered to contain a segmentation violation via the function cJSON_InsertItemInArray at cJSON.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/DaveGamble/cJSON/issues/802"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.debian.org/debian-lts-announce/20... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cjson_project:cjson:1.7.16:*:*:*:*:*:*:*",
"matchCriteriaId": "F689CECB-A7D0-4802-9315-356204983428",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"476"
] | 476 | https://github.com/DaveGamble/cJSON/issues/802 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"DaveGamble",
"cJSON"
] | ### Description
If the the newitem passed in cJSON_InsertItemInArray dont have `prev`, the `newitem->prev`will be null. The null pointer dereference will cause SEGV in function cJSON_InsertItemInArray cJSON.c:2287
### Version
```
commit cb8693b058ba302f4829ec6d03f609ac6f848546 (HEAD -> master, tag: v1.7.16, o... | bug for cJSON_InsertItemInArray function | https://api.github.com/repos/DaveGamble/cJSON/issues/802/comments | 4 | 2023-12-04T07:33:34Z | 2023-12-22T08:21:14Z | https://github.com/DaveGamble/cJSON/issues/802 | 2,023,209,854 | 802 | 5,817 |
CVE-2023-50472 | 2023-12-14T20:15:53.180 | cJSON v1.7.16 was discovered to contain a segmentation violation via the function cJSON_SetValuestring at cJSON.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/DaveGamble/cJSON/issues/803"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cjson_project:cjson:1.7.16:*:*:*:*:*:*:*",
"matchCriteriaId": "F689CECB-A7D0-4802-9315-356204983428",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"476"
] | 476 | https://github.com/DaveGamble/cJSON/issues/803 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"DaveGamble",
"cJSON"
] | ### Description
If the the object passed in cJSON_SetValuestring dont have `valuestring`, the `object->valuestring`will be null. The null pointer dereference will cause SEGV in function cJSON_SetValuestring cJSON.c:408
### Version
```
commit cb8693b058ba302f4829ec6d03f609ac6f848546 (HEAD -> master, tag: v1.7.... | bug for cJSON_SetValuestring | https://api.github.com/repos/DaveGamble/cJSON/issues/803/comments | 4 | 2023-12-04T08:51:18Z | 2023-12-18T03:48:00Z | https://github.com/DaveGamble/cJSON/issues/803 | 2,023,332,797 | 803 | 5,818 |
CVE-2023-6886 | 2023-12-17T01:15:27.307 | A vulnerability was found in xnx3 wangmarket 6.1. It has been rated as critical. Affected by this issue is some unknown functionality of the component Role Management Page. The manipulation leads to code injection. The attack may be launched remotely. The exploit has been disclosed to the public and may be used. VDB-24... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "MULTIPLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PAR... | [
{
"source": "cna@vuldb.com",
"tags": [
"Not Applicable"
],
"url": "https://github.com/xnx3/wangmarket/issues/8"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory"
],
"url": "https://vuldb.com/?ctiid.248246"
},
{
"sou... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wang.market:wangmarket:6.1:*:*:*:*:*:*:*",
"matchCriteriaId": "4C1E04C7-12E0-4F30-905F-EB779F9B1234",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"94"
] | 94 | https://github.com/xnx3/wangmarket/issues/8 | [
"Not Applicable"
] | github.com | [
"xnx3",
"wangmarket"
] | The css exists in role management


| Cross Site Scripting | https://api.github.com/repos/xnx3/wangmarket/issues/8/comments | 2 | 2023-11-29T06:27:11Z | 2023-12-12T12:13:16Z | https://github.com/xnx3/wangmarket/issues/8 | 2,015,905,927 | 8 | 5,819 |
CVE-2023-50965 | 2023-12-17T02:15:21.267 | In MicroHttpServer (aka Micro HTTP Server) through 4398570, _ReadStaticFiles in lib/middleware.c allows a stack-based buffer overflow and potentially remote code execution via a long URI. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
],
"url": "https://github.com/starnight/MicroHttpServer/issues/5"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:starnight:micro_http_server:-:*:*:*:*:*:*:*",
"matchCriteriaId": "1464DBE3-B59A-4C81-A17F-DD3F18EB7AFC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/starnight/MicroHttpServer/issues/5 | [
"Exploit",
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
] | github.com | [
"starnight",
"MicroHttpServer"
] | Hi
After executing my fuzz tests, I discovered a remote stack buffer overflow in the C version of MicroHttpServer in the function uint8_t _ReadStaticFiles(HTTPReqMessage *req, HTTPResMessage *res) at lib/middleware.c, line 67:
https://github.com/starnight/MicroHttpServer/blob/43985708ef5fe7677392c54e229bd22e136c2... | Remote Buffer Overflow at lib/middleware.c | https://api.github.com/repos/starnight/MicroHttpServer/issues/5/comments | 1 | 2023-12-15T01:39:17Z | 2023-12-18T15:01:58Z | https://github.com/starnight/MicroHttpServer/issues/5 | 2,042,748,811 | 5 | 5,820 |
CVE-2023-50976 | 2023-12-18T00:15:11.253 | Redpanda before 23.1.21 and 23.2.x before 23.2.18 has missing authorization checks in the Transactions API. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Release Notes"
],
"url": "https://github.com/redpanda-data/redpanda/compare/v23.1.20...v23.1.21"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes"
],
"url": "https://github.com/redpanda-data/redpanda/compare/v23.2.17...v... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redpanda:redpanda:*:*:*:*:*:*:*:*",
"matchCriteriaId": "386702E5-3A32-414E-996E-694309A84427",
"versionEndExcluding": "23.1.21",
"versionEndIncluding": null,
"versionStartExc... | [
"862"
] | 862 | https://github.com/redpanda-data/redpanda/issues/15048 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"redpanda-data",
"redpanda"
] | Backport https://github.com/redpanda-data/redpanda/pull/14969 to branch v23.1.x. Note that this issue was created as a placeholder, since the original PR's commit(s) could not be automatically cherry-picked.
Here are the commands to execute:
```
git checkout v23.1.x
git checkout -b vbotbuildovich/backport-14969... | [v23.1.x] Transactions API Authorization | https://api.github.com/repos/redpanda-data/redpanda/issues/15048/comments | 1 | 2023-11-20T15:56:01Z | 2023-12-12T12:41:47Z | https://github.com/redpanda-data/redpanda/issues/15048 | 2,002,513,380 | 15,048 | 5,821 |
CVE-2023-50979 | 2023-12-18T04:15:50.970 | Crypto++ (aka cryptopp) through 8.9.0 has a Marvin side channel during decryption with PKCS#1 v1.5 padding. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"int... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/weidai11/cryptopp/issues/1247"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/weidai11/cryptopp/issues/1247"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cryptopp:crypto\\+\\+:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CE3A7AA7-A0EF-4363-A9D8-D1D31498B936",
"versionEndExcluding": null,
"versionEndIncluding": "8.9.0",
"versionStartE... | [
"203"
] | 203 | https://github.com/weidai11/cryptopp/issues/1247 | [
"Exploit"
] | github.com | [
"weidai11",
"cryptopp"
] | ### Crypto++ Issue Report
I've verified that the Crypto++ is vulnerable to the [Marvin Attack](https://people.redhat.com/~hkario/marvin/)—a timing variant of the well-known Bleichenbacher attack.
I've executed the test on ArchLinux, using crypto++ 8.9.0 from the Arch repository.
The reproducer is available in th... | Crypto++ vulnerable to the Marvin Attack | https://api.github.com/repos/weidai11/cryptopp/issues/1247/comments | 1 | 2023-11-12T12:57:41Z | 2024-01-29T00:45:42Z | https://github.com/weidai11/cryptopp/issues/1247 | 1,989,391,420 | 1,247 | 5,822 |
CVE-2023-50981 | 2023-12-18T04:15:51.147 | ModularSquareRoot in Crypto++ (aka cryptopp) through 8.9.0 allows attackers to cause a denial of service (infinite loop) via crafted DER public-key data associated with squared odd numbers, such as the square of 268995137513890432434389773128616504853. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/weidai11/cryptopp/issues/1249"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/weida... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cryptopp:crypto\\+\\+:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CE3A7AA7-A0EF-4363-A9D8-D1D31498B936",
"versionEndExcluding": null,
"versionEndIncluding": "8.9.0",
"versionStartE... | [
"835"
] | 835 | https://github.com/weidai11/cryptopp/issues/1249 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"weidai11",
"cryptopp"
] | Hi, recently I found a security issue in the [ModularSquareRoot](https://github.com/weidai11/cryptopp/blob/3e3b8af96d4d957b77588be91df7715efbe2ed69/nbtheory.cpp#L544) function of `Crypto++` library that would cause an infinite loop, since this function is being used in [ECP::DecodePoint](https://github.com/weidai11/cry... | A security issue in the `ModularSquareRoot` function leads to a DOS attack | https://api.github.com/repos/weidai11/cryptopp/issues/1249/comments | 10 | 2023-11-20T11:59:01Z | 2025-01-05T00:57:25Z | https://github.com/weidai11/cryptopp/issues/1249 | 2,002,042,178 | 1,249 | 5,823 |
CVE-2023-3430 | 2023-12-18T14:15:08.113 | A vulnerability was found in OpenImageIO, where a heap buffer overflow exists in the src/gif.imageio/gifinput.cpp file. This flaw allows a remote attacker to pass a specially crafted file to the application, which triggers a heap-based buffer overflow and could cause a crash, leading to a denial of service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=2218380"
},
{
"source": "nvd@nist.gov",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openimageio:openimageio:2.4.11:*:*:*:*:*:*:*",
"matchCriteriaId": "1026CE08-F9A9-4AE9-9C58-B20DE134CFAD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"787"
] | 787 | https://github.com/AcademySoftwareFoundation/OpenImageIO/issues/3840 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"AcademySoftwareFoundation",
"OpenImageIO"
] | Describe the bug:
Hi, I found heap-buffer-overflow in file src/gif.imageio/gifinput.cpp, line 368.
To Reproduce:
Steps to reproduce the behavior:
1. CC=afl-clang-fast CXX=afl-clang-fast++ CFLAGS="-gdwarf-2 -g3 -O0 -fsanitize=address -fno-omit-frame-pointer" CXXFLAGS="-gdwarf-2 -g3 -O0 -fsanitize=address -fno-omit... | heap-buffer-overflow in file src/gif.imageio/gifinput.cpp, line 368 | https://api.github.com/repos/AcademySoftwareFoundation/OpenImageIO/issues/3840/comments | 13 | 2023-05-15T11:55:43Z | 2024-09-05T17:39:38Z | https://github.com/AcademySoftwareFoundation/OpenImageIO/issues/3840 | 1,709,938,318 | 3,840 | 5,824 |
CVE-2023-48795 | 2023-12-18T16:15:10.897 | The SSH transport protocol with certain OpenSSH extensions, found in OpenSSH before 9.6 and other products, allows remote attackers to bypass integrity checks such that some packets are omitted (from the extension negotiation message), and a client and server may consequently end up with a connection for which some sec... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"int... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/176280/Terrapin-SSH-Connection-Weakening.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openbsd:openssh:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5308FBBB-F738-41C5-97A4-E40118E957CD",
"versionEndExcluding": "9.6",
"versionEndIncluding": null,
"versionStartExcluding... | [
"354"
] | 354 | https://github.com/PowerShell/Win32-OpenSSH/issues/2189 | [
"Issue Tracking"
] | github.com | [
"PowerShell",
"Win32-OpenSSH"
] | ### Summary of the new feature / enhancement
As an administrator, I'd like to know whether my fleet is vulnerable to the [terrapin attack](https://terrapin-attack.com/).
### Proposed technical implementation details (optional)
_No response_ | Clarify exposure to CVE-2023-48795 (Terrapin) | https://api.github.com/repos/PowerShell/Win32-OpenSSH/issues/2189/comments | 9 | 2023-12-21T08:42:41Z | 2024-03-02T23:04:53Z | https://github.com/PowerShell/Win32-OpenSSH/issues/2189 | 2,051,970,807 | 2,189 | 5,825 |
CVE-2023-48795 | 2023-12-18T16:15:10.897 | The SSH transport protocol with certain OpenSSH extensions, found in OpenSSH before 9.6 and other products, allows remote attackers to bypass integrity checks such that some packets are omitted (from the extension negotiation message), and a client and server may consequently end up with a connection for which some sec... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"int... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/176280/Terrapin-SSH-Connection-Weakening.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openbsd:openssh:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5308FBBB-F738-41C5-97A4-E40118E957CD",
"versionEndExcluding": "9.6",
"versionEndIncluding": null,
"versionStartExcluding... | [
"354"
] | 354 | https://github.com/apache/mina-sshd/issues/445 | [
"Issue Tracking"
] | github.com | [
"apache",
"mina-sshd"
] | ### Description
Hello,
is Mina or any contributor planning to work on adding the new OpenSSH protocol extension "strict-KEX" for mitigating Terrapin attacks?
Also did somebody check for the counter overflow conditions mentioned in the advanced counter manupulation section of the paper?
BTW: when implementing ... | Terrapin Mitigation: "strict-kex" | https://api.github.com/repos/apache/mina-sshd/issues/445/comments | 13 | 2023-12-19T09:10:38Z | 2024-01-15T14:48:44Z | https://github.com/apache/mina-sshd/issues/445 | 2,048,232,109 | 445 | 5,826 |
CVE-2023-48795 | 2023-12-18T16:15:10.897 | The SSH transport protocol with certain OpenSSH extensions, found in OpenSSH before 9.6 and other products, allows remote attackers to bypass integrity checks such that some packets are omitted (from the extension negotiation message), and a client and server may consequently end up with a connection for which some sec... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"int... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/176280/Terrapin-SSH-Connection-Weakening.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openbsd:openssh:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5308FBBB-F738-41C5-97A4-E40118E957CD",
"versionEndExcluding": "9.6",
"versionEndIncluding": null,
"versionStartExcluding... | [
"354"
] | 354 | https://github.com/cyd01/KiTTY/issues/520 | [
"Issue Tracking"
] | github.com | [
"cyd01",
"KiTTY"
] | What are the plans to mitigate the [Terrapin vulnerability](https://terrapin-attack.com)? Putty released version 0.80 two days ago with a fix and it appears that BOTH server and client SSH implementations must use the mitigation or the MITM attack is still a threat. As far as I can tell based on the information that ... | Terrapin vulnerability mitigation | https://api.github.com/repos/cyd01/KiTTY/issues/520/comments | 5 | 2023-12-20T05:44:33Z | 2024-08-07T02:03:44Z | https://github.com/cyd01/KiTTY/issues/520 | 2,049,878,873 | 520 | 5,827 |
CVE-2023-48795 | 2023-12-18T16:15:10.897 | The SSH transport protocol with certain OpenSSH extensions, found in OpenSSH before 9.6 and other products, allows remote attackers to bypass integrity checks such that some packets are omitted (from the extension negotiation message), and a client and server may consequently end up with a connection for which some sec... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"int... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/176280/Terrapin-SSH-Connection-Weakening.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openbsd:openssh:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5308FBBB-F738-41C5-97A4-E40118E957CD",
"versionEndExcluding": "9.6",
"versionEndIncluding": null,
"versionStartExcluding... | [
"354"
] | 354 | https://github.com/hierynomus/sshj/issues/916 | [
"Issue Tracking"
] | github.com | [
"hierynomus",
"sshj"
] | Hi!
Is this library affected by the [Terrapin Vulnerability](https://nvd.nist.gov/vuln/detail/CVE-2023-48795) ?
I tried this library with [Terrapin-Scanner](https://github.com/RUB-NDS/Terrapin-Scanner) and the output of the scanner says that SSHJ is affected:
```
G:\Downloads>Terrapin_Scanner_Windows_amd64.exe ... | Terrapin Vulnerability CVE-2023-48795 | https://api.github.com/repos/hierynomus/sshj/issues/916/comments | 1 | 2023-12-19T16:14:44Z | 2023-12-29T12:40:30Z | https://github.com/hierynomus/sshj/issues/916 | 2,048,986,729 | 916 | 5,828 |
CVE-2023-48795 | 2023-12-18T16:15:10.897 | The SSH transport protocol with certain OpenSSH extensions, found in OpenSSH before 9.6 and other products, allows remote attackers to bypass integrity checks such that some packets are omitted (from the extension negotiation message), and a client and server may consequently end up with a connection for which some sec... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"int... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/176280/Terrapin-SSH-Connection-Weakening.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openbsd:openssh:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5308FBBB-F738-41C5-97A4-E40118E957CD",
"versionEndExcluding": "9.6",
"versionEndIncluding": null,
"versionStartExcluding... | [
"354"
] | 354 | https://github.com/janmojzis/tinyssh/issues/81 | [
"Issue Tracking"
] | github.com | [
"janmojzis",
"tinyssh"
] | Hi
tinyssh seems prone to the Terrapin Attack (CVE-2023-48795) as well.
Details on: https://terrapin-attack.com/
Testing a recent version:
```
================================================================================
==================================== Report ====================================
... | CVE-2023-48795 / Terrapin Attack | https://api.github.com/repos/janmojzis/tinyssh/issues/81/comments | 3 | 2023-12-19T19:49:22Z | 2025-01-17T14:04:27Z | https://github.com/janmojzis/tinyssh/issues/81 | 2,049,337,238 | 81 | 5,829 |
CVE-2023-48795 | 2023-12-18T16:15:10.897 | The SSH transport protocol with certain OpenSSH extensions, found in OpenSSH before 9.6 and other products, allows remote attackers to bypass integrity checks such that some packets are omitted (from the extension negotiation message), and a client and server may consequently end up with a connection for which some sec... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"int... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/176280/Terrapin-SSH-Connection-Weakening.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openbsd:openssh:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5308FBBB-F738-41C5-97A4-E40118E957CD",
"versionEndExcluding": "9.6",
"versionEndIncluding": null,
"versionStartExcluding... | [
"354"
] | 354 | https://github.com/mwiede/jsch/issues/457 | [
"Issue Tracking"
] | github.com | [
"mwiede",
"jsch"
] | I would like to know if jsch is affected by the Terrapin attack (https://terrapin-attack.com/).
From what I read about the attack I assume jsch is possibly vulnerable to it (if the right ciphers are used).
Thank you for your fork of jsch. | Is jsch affected by the Terrapin attack? | https://api.github.com/repos/mwiede/jsch/issues/457/comments | 9 | 2023-12-18T18:08:28Z | 2024-02-26T12:20:08Z | https://github.com/mwiede/jsch/issues/457 | 2,047,181,689 | 457 | 5,830 |
CVE-2023-48795 | 2023-12-18T16:15:10.897 | The SSH transport protocol with certain OpenSSH extensions, found in OpenSSH before 9.6 and other products, allows remote attackers to bypass integrity checks such that some packets are omitted (from the extension negotiation message), and a client and server may consequently end up with a connection for which some sec... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"int... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/176280/Terrapin-SSH-Connection-Weakening.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openbsd:openssh:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5308FBBB-F738-41C5-97A4-E40118E957CD",
"versionEndExcluding": "9.6",
"versionEndIncluding": null,
"versionStartExcluding... | [
"354"
] | 354 | https://github.com/paramiko/paramiko/issues/2337 | [
"Issue Tracking"
] | github.com | [
"paramiko",
"paramiko"
] | This is just a tracking ticket to note that we are aware of the issue described here: https://terrapin-attack.com/ - and have been working with the researchers to release a new Paramiko version that mitigates the described attack pattern.
We expect to put out Paramiko 3.4 within the next day or so. The work in progr... | "Terrapin" MitM attack / CVE-2023-48795 | https://api.github.com/repos/paramiko/paramiko/issues/2337/comments | 8 | 2023-12-18T16:21:20Z | 2024-01-11T17:33:01Z | https://github.com/paramiko/paramiko/issues/2337 | 2,047,012,116 | 2,337 | 5,831 |
CVE-2023-48795 | 2023-12-18T16:15:10.897 | The SSH transport protocol with certain OpenSSH extensions, found in OpenSSH before 9.6 and other products, allows remote attackers to bypass integrity checks such that some packets are omitted (from the extension negotiation message), and a client and server may consequently end up with a connection for which some sec... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"int... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/176280/Terrapin-SSH-Connection-Weakening.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openbsd:openssh:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5308FBBB-F738-41C5-97A4-E40118E957CD",
"versionEndExcluding": "9.6",
"versionEndIncluding": null,
"versionStartExcluding... | [
"354"
] | 354 | https://github.com/proftpd/proftpd/issues/456 | [
"Issue Tracking"
] | github.com | [
"proftpd",
"proftpd"
] | The `mod_sftp` module should implement support for the ["chacha20-poly1305@openssh.com"](https://tools.ietf.org/html/draft-josefsson-ssh-chacha20-poly1305-openssh-00) cipher, for performance and interoperability. | Support the chacha20-poly1305@openssh.com SSH cipher | https://api.github.com/repos/proftpd/proftpd/issues/456/comments | 2 | 2017-03-18T17:33:10Z | 2023-10-02T02:15:30Z | https://github.com/proftpd/proftpd/issues/456 | 215,208,862 | 456 | 5,832 |
CVE-2023-48795 | 2023-12-18T16:15:10.897 | The SSH transport protocol with certain OpenSSH extensions, found in OpenSSH before 9.6 and other products, allows remote attackers to bypass integrity checks such that some packets are omitted (from the extension negotiation message), and a client and server may consequently end up with a connection for which some sec... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"int... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/176280/Terrapin-SSH-Connection-Weakening.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openbsd:openssh:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5308FBBB-F738-41C5-97A4-E40118E957CD",
"versionEndExcluding": "9.6",
"versionEndIncluding": null,
"versionStartExcluding... | [
"354"
] | 354 | https://github.com/ssh-mitm/ssh-mitm/issues/165 | [
"Issue Tracking"
] | github.com | [
"ssh-mitm",
"ssh-mitm"
] | I am reaching out to explore a potential similarity I noticed in packet handling between SSH-MITM and the Terrapin Attack, as highlighted in the discussion of Pull Request [#163](https://github.com/ssh-mitm/ssh-mitm/pull/163#issuecomment-1867323311) on the SSH-MITM repository.
It appears that both methods involve di... | Terrapin Attack vs. SSH-MITM: Comparing Packet Handling | https://api.github.com/repos/ssh-mitm/ssh-mitm/issues/165/comments | 4 | 2023-12-22T09:05:00Z | 2025-06-10T09:56:31Z | https://github.com/ssh-mitm/ssh-mitm/issues/165 | 2,053,609,745 | 165 | 5,833 |
CVE-2023-49006 | 2023-12-19T10:15:07.883 | Cross Site Request Forgery (CSRF) vulnerability in Phpsysinfo version 3.4.3 allows a remote attacker to obtain sensitive information via a crafted page in the XML.php file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/Hebing123/cve/issues/5"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/phpsysinfo/phpsysinfo/commit/4f2cee505e4f2e9b369a321063ff2c5e... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phpsysinfo:phpsysinfo:3.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "E23F0F66-F333-46A3-97D0-044CB005C884",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"352"
] | 352 | https://github.com/Hebing123/cve/issues/5 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"Hebing123",
"cve"
] | ### **Description**
phpsysinfo v3.4.3 has JSONP vulnerability.The XML.php file has a JSONP hijacking vulnerability. When a user visits a page carefully crafted by the attacker, the JSON data is obtained and sent to the attacker.
### **Proof of Concept**
We created an HTML file as a proof of concept to showcase the... | XML.php JSONP hijacking in phpsysinfo v3.4.3 | https://api.github.com/repos/Hebing123/cve/issues/5/comments | 1 | 2023-12-15T07:09:51Z | 2024-03-11T06:23:33Z | https://github.com/Hebing123/cve/issues/5 | 2,043,028,601 | 5 | 5,834 |
CVE-2023-49489 | 2023-12-19T10:15:07.943 | Reflective Cross Site Scripting (XSS) vulnerability in KodExplorer version 4.51, allows attackers to obtain sensitive information and escalate privileges via the APP_HOST parameter at config/i18n/en/main.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/kalcaddle/KodExplorer/issues/526"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kodcloud:kodexplorer:4.51:*:*:*:*:*:*:*",
"matchCriteriaId": "C60D895F-51BD-4FAF-B449-B04037016307",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/kalcaddle/KodExplorer/issues/526 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"kalcaddle",
"KodExplorer"
] | ```
GET /index.php?user/login HTTP/1.1
Host: 192.168.160.130:6699
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/116.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;... | KodExplorer 4.51 has a reflective XSS vulnerability | https://api.github.com/repos/kalcaddle/KodExplorer/issues/526/comments | 2 | 2023-11-23T02:19:38Z | 2024-08-27T06:54:59Z | https://github.com/kalcaddle/KodExplorer/issues/526 | 2,007,380,518 | 526 | 5,835 |
CVE-2023-50044 | 2023-12-20T09:15:07.297 | Cesanta MJS 2.20.0 has a getprop_builtin_foreign out-of-bounds read if a Built-in API name occurs in a substring of an input string. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/cesanta/mjs/issues/254"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/cesanta/mjs/pull/255"
},
{
"source": "af854a3a-2127-4... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:2.22.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56AA92AF-E8DC-45C1-9BD0-9511720BD225",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"120"
] | 120 | https://github.com/cesanta/mjs/issues/254 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"cesanta",
"mjs"
] | ## Environment
Ubuntu 22.04.3 LTS
## Compiler
clang version 11.0.0
Target: x86_64-unknown-linux-gnu
Thread model: posix
## Affected Version
mjs 2.20.0
## Step to reproduce
```git clone https://github.com/cesanta/mjs.git
cd mjs
git checkout b1b6eac6b1e5b830a5cb14f8f4dc690ef3162551
export LDFLAGS="-... | Segmentation Fault in getprop_builtin_foreign | https://api.github.com/repos/cesanta/mjs/issues/254/comments | 1 | 2023-11-23T03:20:25Z | 2023-12-27T18:24:10Z | https://github.com/cesanta/mjs/issues/254 | 2,007,422,344 | 254 | 5,836 |
CVE-2023-50628 | 2023-12-20T09:15:07.350 | Buffer Overflow vulnerability in libming version 0.4.8, allows attackers to execute arbitrary code and obtain sensitive information via parser.c component. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/libming/libming/issues/289"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/libming/libming/pull/290"
},
{
"source": "af854a3... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libming:libming:0.4.8:*:*:*:*:*:*:*",
"matchCriteriaId": "DD92BC79-2548-4C6F-9BDD-26C12BDF68AC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"120"
] | 120 | https://github.com/libming/libming/issues/289 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"libming",
"libming"
] | ## Environment
Ubuntu 22.04.3 LTS
## Compiler
clang version 11.0.0
Target: x86_64-unknown-linux-gnu
Thread model: posix
## Affected Version
libming 0.4.8
## Step to reproduce
```cd libming
./autogen.sh
./configure --disable-shared --disable-freetype
cd util
./swftophp <PoC file>
```
## Contents of PoC f... | Memory leaks at parser.c:2353:51 | https://api.github.com/repos/libming/libming/issues/289/comments | 1 | 2023-12-07T19:49:34Z | 2023-12-20T01:44:57Z | https://github.com/libming/libming/issues/289 | 2,031,418,685 | 289 | 5,837 |
CVE-2023-46131 | 2023-12-21T00:15:25.813 | Grails is a framework used to build web applications with the Groovy programming language. A specially crafted web request can lead to a JVM crash or denial of service. Any Grails framework application using Grails data binding is vulnerable. This issue has been patched in version 3.3.17, 4.1.3, 5.3.4, 6.1.0.
| {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/grails/grails-core/commit/74326bdd2cf7dcb594092165e9464520f8366c60"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/grails/gr... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:grails:grails:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CAD6356E-B39D-4EA5-A9FB-D8140235D2B2",
"versionEndExcluding": "3.3.17",
"versionEndIncluding": null,
"versionStartExcludin... | [
"400"
] | 400 | https://github.com/grails/grails-core/issues/13302 | [
"Issue Tracking"
] | github.com | [
"grails",
"grails-core"
] | A vulnerability in the Grails® framework has been identified and patched. For details, please see [the blog post](https://grails.org/blog/2023-12-20-cve-data-binding-dos.html) announcing the vulnerability and the published [security advisory](https://github.com/grails/grails-core/security/advisories/GHSA-3pjv-r7w4-2cf5... | CVE-2023-46131 Discussion | https://api.github.com/repos/apache/grails-core/issues/13302/comments | 20 | 2023-12-19T15:52:34Z | 2024-05-08T19:21:42Z | https://github.com/apache/grails-core/issues/13302 | 2,048,940,040 | 13,302 | 5,838 |
CVE-2023-50473 | 2023-12-21T11:15:08.300 | Cross-Site Scripting (XSS) vulnerability in bill-ahmed qbit-matUI version 1.16.4, allows remote attackers to obtain sensitive information via fixed session identifiers (SID) in index.js file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/bill-ahmed/qbit-matUI/issues/207"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/tianjk99/Cryptographic-Misuses/blob/main/CVE-2023-504... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:billahmed:qbit_matui:1.16.4:*:*:*:*:*:*:*",
"matchCriteriaId": "5C49AEFE-02A9-43F6-8D34-A7A6A974223A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"79"
] | 79 | https://github.com/bill-ahmed/qbit-matUI/issues/207 | [
"Issue Tracking"
] | github.com | [
"bill-ahmed",
"qbit-matUI"
] | The code snippet in the file "mock_backend/index.js" includes a login endpoint ("/api/v2/auth/login") that sets a fixed session identifier (SID) in a cookie. This fixed value of "8c212779b4abde7A" may raise security concerns and need to be addressed.
`res.cookie('SID', '8c212779b4abde7A');`
To address this issue, i... | Fixed Session Identifier in Login Cookie | https://api.github.com/repos/bill-ahmed/qbit-matUI/issues/207/comments | 0 | 2023-12-04T07:41:30Z | 2023-12-04T07:41:30Z | https://github.com/bill-ahmed/qbit-matUI/issues/207 | 2,023,221,178 | 207 | 5,839 |
CVE-2023-50475 | 2023-12-21T11:15:08.673 | An issue was discovered in bcoin-org bcoin version 2.2.0, allows remote attackers to obtain sensitive information via weak hashing algorithms in the component \vendor\faye-websocket.js. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 9.1,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/bcoin-org/bcoin/issues/1174"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/tianjk99/Cryptographic-Misuses/blob/main/CVE-2023-50475.md"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bcoin:bcoin:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CB396AC4-3FE6-4757-B077-56CD055BB817",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"327"
] | 327 | https://github.com/bcoin-org/bcoin/issues/1174 | [
"Exploit"
] | github.com | [
"bcoin-org",
"bcoin"
] | Please check if there is any problem with using weak cryptographic algorithms.
The current implementation in the code utilizes the MD5 and SHA1 hash algorithm, which is considered weak and vulnerable to attacks such as collision and preimage attacks. This poses a security risk as it can potentially be exploited by mal... | Use of Weak Hashing Algorithms (MD5 and SHA1) during Client Initialization | https://api.github.com/repos/bcoin-org/bcoin/issues/1174/comments | 2 | 2023-11-30T09:50:22Z | 2024-11-07T17:07:18Z | https://github.com/bcoin-org/bcoin/issues/1174 | 2,018,266,015 | 1,174 | 5,840 |
CVE-2023-50481 | 2023-12-21T11:15:08.790 | An issue was discovered in blinksocks version 3.3.8, allows remote attackers to obtain sensitive information via weak encryption algorithms in the component /presets/ssr-auth-chain.js. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/blinksocks/blinksocks/issues/108"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/tianjk99/Cryptographic-Misuses/blob/main/CVE-2023-504... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:blinksocks:blinksocks:3.3.8:*:*:*:*:*:*:*",
"matchCriteriaId": "7FCA3BC9-233F-4F3A-8069-2A56BF277495",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"327"
] | 327 | https://github.com/blinksocks/blinksocks/issues/108 | [
"Issue Tracking"
] | github.com | [
"blinksocks",
"blinksocks"
] | Some code snippets in the project use outdated encryption algorithms and fixed initialization vectors, which may lead to security vulnerabilities. It is recommended to improve the security and data integrity of the system by updating the encryption algorithm and initialization vector.
Using the non-random IV for CBC... | Bug Report:Usage of Outdated Encryption Algorithm and Fixed Initialization Vector | https://api.github.com/repos/blinksocks/blinksocks/issues/108/comments | 0 | 2023-12-04T12:50:12Z | 2023-12-04T12:50:12Z | https://github.com/blinksocks/blinksocks/issues/108 | 2,023,785,927 | 108 | 5,841 |
CVE-2023-50724 | 2023-12-21T15:15:10.573 | Resque (pronounced like "rescue") is a Redis-backed library for creating background jobs, placing those jobs on multiple queues, and processing them later. resque-web in resque versions before 2.1.0 are vulnerable to reflected XSS through the current_queue parameter in the path of the queues endpoint. This issue has be... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
],
"url": "https://github.com/resque/resque/issues/1679"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:resque:resque:*:*:*:*:*:ruby:*:*",
"matchCriteriaId": "3748B26E-DE1D-4B6B-8A6E-C79BC6DBD0BF",
"versionEndExcluding": "2.1.0",
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/resque/resque/issues/1679 | [
"Exploit",
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
] | github.com | [
"resque",
"resque"
] | `https://example.com/queues/<img src="x" onerror="alert(document.domain)">`
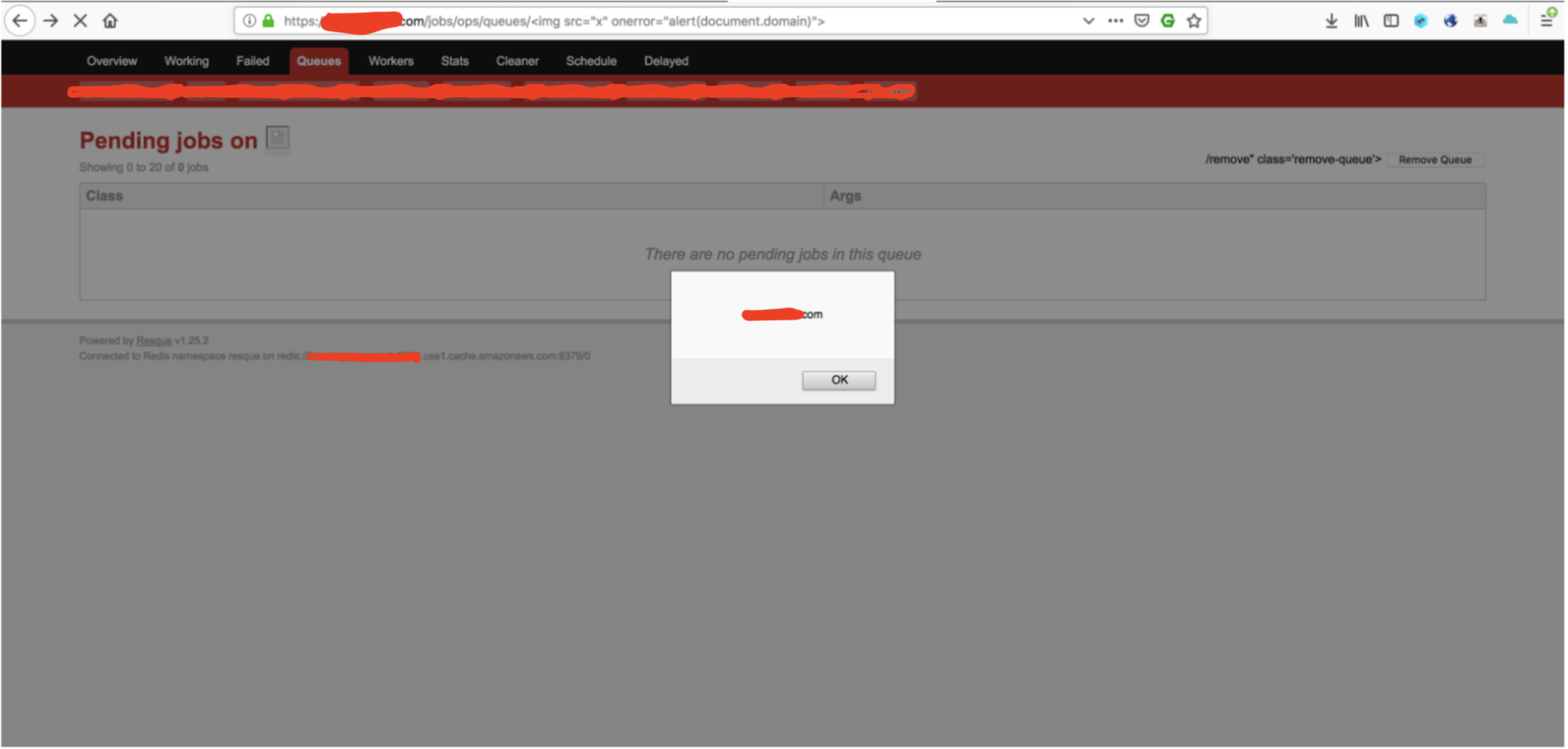
As shown in the image above, the application is vulnerable to Reflected Cross Site Scripting through pathname of the site. Wi... | Vulnerable to Reflected Cross Site Scripting through pathname | https://api.github.com/repos/resque/resque/issues/1679/comments | 0 | 2019-04-17T15:32:11Z | 2021-07-22T03:47:50Z | https://github.com/resque/resque/issues/1679 | 434,348,975 | 1,679 | 5,842 |
CVE-2023-4255 | 2023-12-21T16:15:10.017 | An out-of-bounds write issue has been discovered in the backspace handling of the checkType() function in etc.c within the W3M application. This vulnerability is triggered by supplying a specially crafted HTML file to the w3m binary. Exploitation of this flaw could lead to application crashes, resulting in a denial of ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=2255207"
},
{
"source": "secalert@redhat.com",
"tags": [
"Patch"
],
"url": "https://github.com/tats/w3m/commit/edc602651c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tats:w3m:0.5.3\\+git20230121-1:*:*:*:*:*:*:*",
"matchCriteriaId": "7A31CA22-C625-4E9C-9C57-CCDBC9E9B99A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"787"
] | 787 | https://github.com/tats/w3m/issues/268 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"tats",
"w3m"
] | Hi,
I think the fix for [CVE-2022-38223](https://github.com/advisories/GHSA-rf3p-g68h-h93f) in [419ca82](https://github.com/tats/w3m/commit/419ca82d57c72242817b55e2eaa4cdbf6916e7fa) is not complete and it is still possible to trigger the same bug with a different poc in [tats/w3m#242](https://github.com/tats/w3m/iss... | Incomplete fix for CVE-2022-38223 | https://api.github.com/repos/tats/w3m/issues/268/comments | 8 | 2023-06-12T04:16:49Z | 2023-12-28T19:03:07Z | https://github.com/tats/w3m/issues/268 | 1,751,860,644 | 268 | 5,843 |
CVE-2023-4256 | 2023-12-21T16:15:10.400 | Within tcpreplay's tcprewrite, a double free vulnerability has been identified in the tcpedit_dlt_cleanup() function within plugins/dlt_plugins.c. This vulnerability can be exploited by supplying a specifically crafted file to the tcprewrite binary. This flaw enables a local attacker to initiate a Denial of Service (Do... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=2255212"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "7272A798-456E-43CC-A8D2-33FF2AE16FF7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"415"
] | 415 | https://github.com/appneta/tcpreplay/issues/813 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | **Describe the bug**
tcprewrite in tcpreplay latest commit : [43693c4](https://github.com/appneta/tcpreplay/commit/43693c4a92dda227a5134ae5e71a7247ae345323), v4.4.4 and v.4.4.3 has a double free in function tcpedit_dlt_cleanup in plugins/dlt_plugins.c.
**To Reproduce**
Steps to reproduce the behavior:
1. Get... | [Bug] Double free in tcpedit_dlt_cleanup in tcprewrite | https://api.github.com/repos/appneta/tcpreplay/issues/813/comments | 8 | 2023-07-19T03:25:47Z | 2024-07-23T15:25:41Z | https://github.com/appneta/tcpreplay/issues/813 | 1,811,074,253 | 813 | 5,844 |
CVE-2023-51713 | 2023-12-22T03:15:09.730 | make_ftp_cmd in main.c in ProFTPD before 1.3.8a has a one-byte out-of-bounds read, and daemon crash, because of mishandling of quote/backslash semantics. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Release Notes"
],
"url": "https://github.com/proftpd/proftpd/blob/1.3.8/NEWS"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"url": "https://github.com/prof... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:proftpd:proftpd:*:*:*:*:*:*:*:*",
"matchCriteriaId": "82A8E114-13E4-4799-8838-37D9BB4BB4D1",
"versionEndExcluding": "1.3.8a",
"versionEndIncluding": null,
"versionStartExclud... | [
"125"
] | 125 | https://github.com/proftpd/proftpd/issues/1683 | [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
] | github.com | [
"proftpd",
"proftpd"
] | ### What I Did
Cloned latest version of ProFTPD (5e57d41) in a container running Ubuntu 20.04, configured with flags for ASAN and UBSan.
Started the tool as such `./proftpd -n -c <SOMEDIR>/basic.conf -X`.
Sent over a sequence of packets, gathered from a fuzz campaign using the `aflnet-replay` utility.
### Wha... | Out-of-bounds buffer read when handling FTP commands | https://api.github.com/repos/proftpd/proftpd/issues/1683/comments | 16 | 2023-06-06T05:37:54Z | 2023-09-10T17:25:08Z | https://github.com/proftpd/proftpd/issues/1683 | 1,743,120,578 | 1,683 | 5,845 |
CVE-2023-51713 | 2023-12-22T03:15:09.730 | make_ftp_cmd in main.c in ProFTPD before 1.3.8a has a one-byte out-of-bounds read, and daemon crash, because of mishandling of quote/backslash semantics. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Release Notes"
],
"url": "https://github.com/proftpd/proftpd/blob/1.3.8/NEWS"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"url": "https://github.com/prof... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:proftpd:proftpd:*:*:*:*:*:*:*:*",
"matchCriteriaId": "82A8E114-13E4-4799-8838-37D9BB4BB4D1",
"versionEndExcluding": "1.3.8a",
"versionEndIncluding": null,
"versionStartExclud... | [
"125"
] | 125 | https://github.com/proftpd/proftpd/issues/1683#issuecomment-1712887554 | [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
] | github.com | [
"proftpd",
"proftpd"
] | ### What I Did
Cloned latest version of ProFTPD (5e57d41) in a container running Ubuntu 20.04, configured with flags for ASAN and UBSan.
Started the tool as such `./proftpd -n -c <SOMEDIR>/basic.conf -X`.
Sent over a sequence of packets, gathered from a fuzz campaign using the `aflnet-replay` utility.
### Wha... | Out-of-bounds buffer read when handling FTP commands | https://api.github.com/repos/proftpd/proftpd/issues/1683/comments | 16 | 2023-06-06T05:37:54Z | 2023-09-10T17:25:08Z | https://github.com/proftpd/proftpd/issues/1683 | 1,743,120,578 | 1,683 | 5,846 |
CVE-2023-49391 | 2023-12-22T11:15:07.517 | An issue was discovered in free5GC version 3.3.0, allows remote attackers to execute arbitrary code and cause a denial of service (DoS) on AMF component via crafted NGAP message. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/free5gc/free5gc/issues/497"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:free5gc:free5gc:3.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "89BA8BA8-E366-48F9-930A-91ED1442AAFE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"94"
] | 94 | https://github.com/free5gc/free5gc/issues/497 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"free5gc",
"free5gc"
] | ## Describe the bug
When testing the free5gc AMF, it always crashes when receiving invalid NGAP messages.
## To Reproduce
Steps to reproduce the behavior:
1. Use https://github.com/free5gc/free5gc-compose as the test target
2. Start it with command `docker compose up`
3. Find the amf address with command `docke... | [Bugs] AMF crashed when receving invalid NGAP messages | https://api.github.com/repos/free5gc/free5gc/issues/497/comments | 1 | 2023-10-25T08:11:58Z | 2023-12-04T09:48:25Z | https://github.com/free5gc/free5gc/issues/497 | 1,960,809,373 | 497 | 5,847 |
CVE-2023-51661 | 2023-12-22T15:15:08.377 | Wasmer is a WebAssembly runtime that enables containers to run anywhere: from Desktop to the Cloud, Edge and even the browser. Wasm programs can access the filesystem outside of the sandbox. Service providers running untrusted Wasm code on Wasmer can unexpectedly expose the host filesystem. This vulnerability has been ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 8.4,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/wasmerio/wasmer/commit/4d63febf9d8b257b0531963b85df48d45d0dbf3c"
},
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/was... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wasmer:wasmer:*:*:*:*:*:rust:*:*",
"matchCriteriaId": "14DB3027-8D4F-47CB-9B0C-9603C74C4299",
"versionEndExcluding": "4.2.4",
"versionEndIncluding": null,
"versionStartExclud... | [
"284"
] | 284 | https://github.com/wasmerio/wasmer/issues/4267 | [
"Issue Tracking"
] | github.com | [
"wasmerio",
"wasmer"
] | In wasmtime or other Wasm runtimes with WASI support, you have to explicit preopen a directory to have access to the host filesystem. With wasmer, it seems the cwd is opened by default.
For example, given this small Rust program:
```
fn main() {
let f = std::fs::OpenOptions::new()
.write(true)
... | Running `*.wasm` files directly doesn't sandbox the filesystem | https://api.github.com/repos/wasmerio/wasmer/issues/4267/comments | 11 | 2023-10-21T20:33:09Z | 2023-12-12T13:02:21Z | https://github.com/wasmerio/wasmer/issues/4267 | 1,955,654,230 | 4,267 | 5,849 |
CVE-2023-51649 | 2023-12-22T17:15:10.197 | Nautobot is a Network Source of Truth and Network Automation Platform built as a web application atop the Django Python framework with a PostgreSQL or MySQL database. When submitting a Job to run via a Job Button, only the model-level `extras.run_job` permission is checked (i.e., does the user have permission to run Jo... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 3.5,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integri... | [
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/nautobot/nautobot/issues/4988"
},
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/nautobot/naut... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:networktocode:nautobot:*:*:*:*:*:*:*:*",
"matchCriteriaId": "882A82E9-9E77-42C7-9BF0-B9043343580F",
"versionEndExcluding": "1.6.8",
"versionEndIncluding": null,
"versionStart... | [
"863"
] | 863 | https://github.com/nautobot/nautobot/issues/4988 | [
"Issue Tracking"
] | github.com | [
"nautobot",
"nautobot"
] | <!--
NOTE: IF YOUR ISSUE DOES NOT FOLLOW THIS TEMPLATE, IT WILL BE CLOSED.
This form is only for reporting reproducible bugs. If you need assistance
with Nautobot installation, or if you have a general question, please start a
discussion instead: https://github.com/nautobot/nautobot/discussions
... | Job and job-button constraints permissions have not been applied | https://api.github.com/repos/nautobot/nautobot/issues/4988/comments | 2 | 2023-12-15T14:29:40Z | 2024-03-20T03:13:29Z | https://github.com/nautobot/nautobot/issues/4988 | 2,043,830,235 | 4,988 | 5,850 |
CVE-2023-7008 | 2023-12-23T13:15:07.573 | A vulnerability was found in systemd-resolved. This issue may allow systemd-resolved to accept records of DNSSEC-signed domains even when they have no signature, allowing man-in-the-middles (or the upstream DNS resolver) to manipulate records. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"int... | [
{
"source": "secalert@redhat.com",
"tags": null,
"url": "https://access.redhat.com/errata/RHSA-2024:2463"
},
{
"source": "secalert@redhat.com",
"tags": null,
"url": "https://access.redhat.com/errata/RHSA-2024:3203"
},
{
"source": "secalert@redhat.com",
"tags": [
"Vendor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:systemd_project:systemd:25:*:*:*:*:*:*:*",
"matchCriteriaId": "64D83463-13ED-430C-8C40-2237DF0E3643",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"300"
] | 300 | https://github.com/systemd/systemd/issues/25676 | [
"Issue Tracking"
] | github.com | [
"systemd",
"systemd"
] | ### systemd version the issue has been seen with
251.8-1-manjaro
### Used distribution
Manjaro
### Linux kernel version used
5.15.81-1-MANJARO
### CPU architectures issue was seen on
x86_64
### Component
systemd-resolved
### Expected behaviour you didn't see
When `DNSSEC=yes` is set and querying a DNSSEC-ena... | resolved DNSSEC validation can be bypassed by MITM | https://api.github.com/repos/systemd/systemd/issues/25676/comments | 68 | 2022-12-08T12:34:18Z | 2024-01-18T12:42:52Z | https://github.com/systemd/systemd/issues/25676 | 1,484,544,284 | 25,676 | 5,851 |
CVE-2023-51771 | 2023-12-25T05:15:08.730 | In MicroHttpServer (aka Micro HTTP Server) through a8ab029, _ParseHeader in lib/server.c allows a one-byte recv buffer overflow via a long URI. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/starnight/MicroHttpServer/issues/8"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://github.com/starnight/MicroHttpServer/tree/a8ab029c9a26a4c9... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:starnight:micro_http_server:-:*:*:*:*:*:*:*",
"matchCriteriaId": "1464DBE3-B59A-4C81-A17F-DD3F18EB7AFC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"120"
] | 120 | https://github.com/starnight/MicroHttpServer/issues/8 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"starnight",
"MicroHttpServer"
] | Hi again!
I discovered a second remote buffer overflow in the C version of MicroHttpServer (through commit a8ab029). This one is an off-by-one global buffer overflow in the function _ParseHeader lib/server.c, line 208:
https://github.com/starnight/MicroHttpServer/blob/a8ab029c9a26a4c9f26b9d8a2757b8299aaff120/c-v... | Remote buffer overflow in lib/server.c | https://api.github.com/repos/starnight/MicroHttpServer/issues/8/comments | 0 | 2023-12-25T01:04:39Z | 2024-02-14T15:34:46Z | https://github.com/starnight/MicroHttpServer/issues/8 | 2,055,264,054 | 8 | 5,852 |
CVE-2023-37185 | 2023-12-25T07:15:08.793 | C-blosc2 before 2.9.3 was discovered to contain a NULL pointer dereference via the function zfp_prec_decompress at zfp/blosc2-zfp.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/Blosc/c-blosc2/commit/425e8a9a59d49378d57e2116b6c9b0190a5986f5"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes"
],
"url": "https://github.com/Blosc/c-blosc2/compare/v2.9.2...v2.9.3"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:c-blosc2_project:c-blosc2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "075116F3-2BB5-414B-82A9-D132E60D4769",
"versionEndExcluding": "2.9.3",
"versionEndIncluding": null,
"versionSt... | [
"476"
] | 476 | https://github.com/Blosc/c-blosc2/issues/519 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"Blosc",
"c-blosc2"
] | **Describe the bug**
Null Pointer Dereferencing at line **391** in [plugins/codecs/zfp/blosc2-zfp.c](https://github.com/Blosc/c-blosc2/blob/86fc0f66aa6dd079dbf79d775dc9dc1462830ffd/plugins/codecs/zfp/blosc2-zfp.c#LL391C29-L391C29). This is caused due to using a pointer to a chunk which does not exist. This bug is in t... | Null Pointer Dereferencing bug in plugins/codecs/zfp/blosc2-zfp.c | https://api.github.com/repos/Blosc/c-blosc2/issues/519/comments | 0 | 2023-06-20T21:10:32Z | 2023-06-21T09:17:02Z | https://github.com/Blosc/c-blosc2/issues/519 | 1,766,176,337 | 519 | 5,853 |
CVE-2023-37186 | 2023-12-25T07:15:08.980 | C-blosc2 before 2.9.3 was discovered to contain a NULL pointer dereference in ndlz/ndlz8x8.c via a NULL pointer to memset. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/Blosc/c-blosc2/commit/d55bfcd6804699e1435dc3e233fd76c8a5d3f9e3"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes"
],
"url": "https://github.com/Blosc/c-blosc2/compare/v2.9.2...v2.9.3"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:c-blosc2_project:c-blosc2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "075116F3-2BB5-414B-82A9-D132E60D4769",
"versionEndExcluding": "2.9.3",
"versionEndIncluding": null,
"versionSt... | [
"476"
] | 476 | https://github.com/Blosc/c-blosc2/issues/522 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"Blosc",
"c-blosc2"
] | **Describe the bug**
Null Pointer Dereferencing at line 465 in [plugins/codecs/ndlz/ndlz8x8.c](https://github.com/Blosc/c-blosc2/blob/86fc0f66aa6dd079dbf79d775dc9dc1462830ffd/plugins/codecs/ndlz/ndlz8x8.c#LL465C5-L465C5). This is caused due to passing a null ptr to `memset`.
**To Reproduce**
Run the fuzzing harnes... | Null Pointer Dereferencing bug in plugins/codecs/ndlz/ndlz8x8.c | https://api.github.com/repos/Blosc/c-blosc2/issues/522/comments | 0 | 2023-06-20T21:22:07Z | 2023-06-21T09:17:58Z | https://github.com/Blosc/c-blosc2/issues/522 | 1,766,209,904 | 522 | 5,854 |
CVE-2023-37187 | 2023-12-25T07:15:09.183 | C-blosc2 before 2.9.3 was discovered to contain a NULL pointer dereference via the zfp/blosc2-zfp.c zfp_acc_decompress. function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/Blosc/c-blosc2/commit/425e8a9a59d49378d57e2116b6c9b0190a5986f5"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes"
],
"url": "https://github.com/Blosc/c-blosc2/compare/v2.9.2...v2.9.3"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:c-blosc2_project:c-blosc2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "075116F3-2BB5-414B-82A9-D132E60D4769",
"versionEndExcluding": "2.9.3",
"versionEndIncluding": null,
"versionSt... | [
"476"
] | 476 | https://github.com/Blosc/c-blosc2/issues/520 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"Blosc",
"c-blosc2"
] | **Describe the bug**
Null Pointer Dereferencing at line **152** in [plugins/codecs/zfp/blosc2-zfp.c](https://github.com/Blosc/c-blosc2/blob/86fc0f66aa6dd079dbf79d775dc9dc1462830ffd/plugins/codecs/zfp/blosc2-zfp.c#LL152C19-L152C19). This is caused due to using a pointer to a chunk which does not exist. This bug is in f... | Null Pointer Dereferencing bug in plugins/codecs/zfp/blosc2-zfp.c | https://api.github.com/repos/Blosc/c-blosc2/issues/520/comments | 0 | 2023-06-20T21:11:25Z | 2023-06-21T09:17:12Z | https://github.com/Blosc/c-blosc2/issues/520 | 1,766,179,764 | 520 | 5,855 |
CVE-2023-37188 | 2023-12-25T07:15:09.347 | C-blosc2 before 2.9.3 was discovered to contain a NULL pointer dereference via the function zfp_rate_decompress at zfp/blosc2-zfp.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/Blosc/c-blosc2/commit/425e8a9a59d49378d57e2116b6c9b0190a5986f5"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes"
],
"url": "https://github.com/Blosc/c-blosc2/compare/v2.9.2...v2.9.3"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:c-blosc2_project:c-blosc2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "075116F3-2BB5-414B-82A9-D132E60D4769",
"versionEndExcluding": "2.9.3",
"versionEndIncluding": null,
"versionSt... | [
"476"
] | 476 | https://github.com/Blosc/c-blosc2/issues/521 | [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
] | github.com | [
"Blosc",
"c-blosc2"
] | **Describe the bug**
Null Pointer Dereferencing at line **641** in [plugins/codecs/zfp/blosc2-zfp.c](https://github.com/Blosc/c-blosc2/blob/86fc0f66aa6dd079dbf79d775dc9dc1462830ffd/plugins/codecs/zfp/blosc2-zfp.c#L641). This is caused due to using a pointer to a chunk which does not exist. This bug is in function `zfp... | Null Pointer Dereferencing bug in plugins/codecs/zfp/blosc2-zfp.c | https://api.github.com/repos/Blosc/c-blosc2/issues/521/comments | 0 | 2023-06-20T21:13:30Z | 2023-06-21T09:17:20Z | https://github.com/Blosc/c-blosc2/issues/521 | 1,766,187,839 | 521 | 5,856 |
CVE-2023-52086 | 2023-12-26T18:15:09.030 | resumable.php (aka PHP backend for resumable.js) 0.1.4 before 3c6dbf5 allows arbitrary file upload anywhere in the filesystem via ../ in multipart/form-data content to upload.php. (File overwrite hasn't been possible with the code available in GitHub in recent years, however.) | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/dilab/resumable.php/commit/3c6dbf5170b01cbb712013c7d0a83f5aac45653b"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/dilab/resumable.php/issues/34"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:startutorial:php_backend_for_resumable.js:0.1.4:*:*:*:*:*:*:*",
"matchCriteriaId": "61A220BB-610D-4B95-AEC7-B4BE6197A87E",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"434"
] | 434 | https://github.com/dilab/resumable.php/issues/34 | [
"Issue Tracking"
] | github.com | [
"dilab",
"resumable.php"
] | Hi @dilab
~~How can I contact you about the security vulnerability I found ?~~
Here is how to reproduce the vulnerability:
```
curl 'https://example.org/upload.php?resumableChunkNumber=1&resumableChunkSize=1048576&resumableCurrentChunkSize=80881&resumableTotalSize=80881&resumableType=&resumableIdentifier=80881... | Security vulnerability - arbitrary file upload anywhere in the file system | https://api.github.com/repos/dilab/resumable.php/issues/34/comments | 7 | 2023-12-07T15:31:30Z | 2023-12-26T23:42:39Z | https://github.com/dilab/resumable.php/issues/34 | 2,031,007,359 | 34 | 5,857 |
CVE-2023-52096 | 2023-12-26T23:15:07.947 | SteVe Community ocpp-jaxb before 0.0.8 generates invalid timestamps such as ones with month 00 in certain situations (such as when an application receives a StartTransaction Open Charge Point Protocol message with a timestamp parameter of 1000000). This may lead to a SQL exception in applications, and may undermine the... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://github.com/steve-community/ocpp-jaxb/compare/0.0.7...0.0.8"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/steve-community/ocpp-jaxb/issues/1... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:steve-community:ocpp-jaxb:*:*:*:*:*:*:*:*",
"matchCriteriaId": "00CEA40C-5001-4C81-A9C8-45DA784BBEEA",
"versionEndExcluding": "0.0.8",
"versionEndIncluding": null,
"versionSt... | [
"89"
] | 89 | https://github.com/steve-community/ocpp-jaxb/issues/13 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"steve-community",
"ocpp-jaxb"
] | The default approach we use causes invalid timestamp values: https://github.com/steve-community/steve/issues/1292
We need a mechanism that closely follows XSD:dateTime and ISO 8601, but also respects some of the flexibilities: optional fractions, optional offset/timezone. | Use a better fitting DateTimeFormatter | https://api.github.com/repos/steve-community/ocpp-jaxb/issues/13/comments | 0 | 2023-12-03T11:22:17Z | 2023-12-03T11:28:04Z | https://github.com/steve-community/ocpp-jaxb/issues/13 | 2,022,476,118 | 13 | 5,858 |
CVE-2023-52096 | 2023-12-26T23:15:07.947 | SteVe Community ocpp-jaxb before 0.0.8 generates invalid timestamps such as ones with month 00 in certain situations (such as when an application receives a StartTransaction Open Charge Point Protocol message with a timestamp parameter of 1000000). This may lead to a SQL exception in applications, and may undermine the... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://github.com/steve-community/ocpp-jaxb/compare/0.0.7...0.0.8"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/steve-community/ocpp-jaxb/issues/1... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:steve-community:ocpp-jaxb:*:*:*:*:*:*:*:*",
"matchCriteriaId": "00CEA40C-5001-4C81-A9C8-45DA784BBEEA",
"versionEndExcluding": "0.0.8",
"versionEndIncluding": null,
"versionSt... | [
"89"
] | 89 | https://github.com/steve-community/steve/issues/1292 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"steve-community",
"steve"
] | #### Checklist
- [x] I checked other issues already, but found no answer/solution
- [x] I checked the documentation and wiki, but found no answer/solution
- [ ] I am running the latest version and the issue still occurs
- [x] I am sure that this issue is about SteVe (and not about the charging station software or... | Inserting Invalid Timestamp Results in '0000-00-00 00:00:00.000000' and Causes SQL Exception | https://api.github.com/repos/steve-community/steve/issues/1292/comments | 2 | 2023-11-07T19:23:52Z | 2023-12-03T11:43:54Z | https://github.com/steve-community/steve/issues/1292 | 1,982,068,484 | 1,292 | 5,859 |
CVE-2023-51075 | 2023-12-27T21:15:08.300 | hutool-core v5.8.23 was discovered to contain an infinite loop in the StrSplitter.splitByRegex function. This vulnerability allows attackers to cause a Denial of Service (DoS) via manipulation of the first two parameters. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dromara/hutool/issues/3421"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hutool:hutool:5.8.23:*:*:*:*:*:*:*",
"matchCriteriaId": "E06EB61A-4250-4F44-9743-3108FF70C157",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"835"
] | 835 | https://github.com/dromara/hutool/issues/3421 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dromara",
"hutool"
] | ### 版本情况
JDK版本: openjdk_8_201
hutool-core版本: 5.8.23
### 问题描述(包括截图)
在使用StrSplitter.splitByRegex函数时,如果前两个参数为“”,无论后两个参数如何设置,执行程序会进入死循环,最终都会导致程序崩溃(OOM or StackOverFlow)。
1. 复现代码
```java
import org.junit.Test;
import cn.hutool.core.text.*;
import java.util.List;
public class StrSplitterFuzzerSplitByReg... | StrSplitter.splitByRegex函数使用过程中出现OOM or StackOverFlow | https://api.github.com/repos/chinabugotech/hutool/issues/3421/comments | 1 | 2023-12-11T12:24:53Z | 2023-12-11T20:29:51Z | https://github.com/chinabugotech/hutool/issues/3421 | 2,035,564,943 | 3,421 | 5,860 |
CVE-2023-51080 | 2023-12-27T21:15:08.397 | The NumberUtil.toBigDecimal method in hutool-core v5.8.23 was discovered to contain a stack overflow. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/dromara/hutool/issues/3423"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hutool:hutool:5.8.23:*:*:*:*:*:*:*",
"matchCriteriaId": "E06EB61A-4250-4F44-9743-3108FF70C157",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/dromara/hutool/issues/3423 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"dromara",
"hutool"
] | ### 版本情况
JDK版本: openjdk_8_201
hutool-core: 5.8.23(请确保最新尝试是否还有问题)
### 问题描述(包括截图)
在hutool-core的5.8.23版本中,调用NumberUtil.toBigDecimal方法时,如果入参为“NaN”,程序会崩溃,报StackOverflowError
1. 复现代码
```java
import org.junit.Test;
import cn.hutool.core.util.*;
import java.math.BigDecimal;
public class NumberUtilFuzzerToB... | NumberUtil.toBigDecimal方法报StackOverflowError | https://api.github.com/repos/chinabugotech/hutool/issues/3423/comments | 2 | 2023-12-13T06:23:42Z | 2024-01-11T02:39:14Z | https://github.com/chinabugotech/hutool/issues/3423 | 2,039,038,848 | 3,423 | 5,861 |
CVE-2023-51084 | 2023-12-27T21:15:08.450 | hyavijava v6.0.07.1 was discovered to contain a stack overflow via the ResultConverter.convert2Xml method. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/PoppingSnack/VulReport/issues/12"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/Po... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yavijava:yavijava:6.0.07.1:*:*:*:*:*:*:*",
"matchCriteriaId": "2B65B9D4-F712-40E8-9651-B632DBD5EFDC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"787"
] | 787 | https://github.com/PoppingSnack/VulReport/issues/12 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"PoppingSnack",
"VulReport"
] | ## Description
An StackOverflowError occurs when I execute the ResultConverter.convert2Xml method in hyavijava v6.0.07.1.
## Error Log
```
java.lang.StackOverflowError
at java.base/java.lang.StringUTF16.checkBoundsOffCount(StringUTF16.java:1482)
at java.base/java.lang.StringUTF16.inflate(StringUTF16.java:13... | An StackOverflowError occurs when I execute the ResultConverter.convert2Xml method in hyavijava v6.0.07.1 | https://api.github.com/repos/PoppingSnack/VulReport/issues/12/comments | 0 | 2023-12-14T09:31:44Z | 2023-12-14T09:31:44Z | https://github.com/PoppingSnack/VulReport/issues/12 | 2,041,298,213 | 12 | 5,862 |
CVE-2023-49469 | 2023-12-28T06:15:44.340 | Reflected Cross Site Scripting (XSS) vulnerability in Shaarli v0.12.2, allows remote attackers to execute arbitrary code via search tag function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/shaarli/Shaarli/issues/2038"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes"
],
"url": "https://github.com/shaarli/Shaarli/releases/tag/v0.13.0"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:shaarli_project:shaarli:0.12.2:*:*:*:*:*:*:*",
"matchCriteriaId": "3FB9DCA3-CDAD-4047-9EEB-D35772A5B4F9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"79"
] | 79 | https://github.com/shaarli/Shaarli/issues/2038 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"shaarli",
"Shaarli"
] | Version v0.12.2
I have identified a Reflected Cross-site Scripting (XSS) vulnerability that could potentially be exploited by attackers to execute malicious code within the context of a user’s web browser.
The vulnerability occurs when unsanitized user input is directly embedded into the HTML output of the search... | Reflected XSS Vulnerability in Search Tag | https://api.github.com/repos/shaarli/Shaarli/issues/2038/comments | 3 | 2023-11-22T12:56:24Z | 2023-11-22T16:56:42Z | https://github.com/shaarli/Shaarli/issues/2038 | 2,006,285,430 | 2,038 | 5,863 |
CVE-2023-50692 | 2023-12-28T06:15:44.400 | File Upload vulnerability in JIZHICMS v.2.5, allows remote attacker to execute arbitrary code via a crafted file uploaded and downloaded to the download_url parameter in the app/admin/exts/ directory. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/Cherry-toto/jizhicms/issues/91"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/Cher... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jizhicms:jizhicms:2.5:*:*:*:*:*:*:*",
"matchCriteriaId": "664B42DA-E99F-4635-A831-84CB9B9EA165",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"434"
] | 434 | https://github.com/Cherry-toto/jizhicms/issues/91 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"Cherry-toto",
"jizhicms"
] | **Vulnerability recurrence:**
1. Construct a PHP sentence and then compress it in zip format through the compressed package

2. Upload the zip to the VPS server and use python on the VPS to start an http servi... | JIZHICMS V2.5 has background Arbitrary File Downloads causing RCE | https://api.github.com/repos/Cherry-toto/jizhicms/issues/91/comments | 3 | 2023-12-10T17:23:12Z | 2024-08-27T12:40:18Z | https://github.com/Cherry-toto/jizhicms/issues/91 | 2,034,459,693 | 91 | 5,864 |
CVE-2023-52152 | 2023-12-28T23:15:44.197 | mupnp/net/uri.c in mUPnP for C through 3.0.2 has an out-of-bounds read and application crash because it lacks a certain host length recalculation. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/cybergarage/mupnp/issues/21"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/cyberga... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cybergarage:mupnp_for_c:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0A5EE1C0-3244-4748-96E7-82FCE547D2F5",
"versionEndExcluding": null,
"versionEndIncluding": "3.0.2",
"versionStar... | [
"125"
] | 125 | https://github.com/cybergarage/mupnp/issues/21 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"cybergarage",
"mupnp"
] | Note: this all based on latest master branch. I used default configure options except I built with ASAN when fuzzing
. Given that a basic HTTP server (which does not even consider the request) is affected, I assume anything that uses this HTTP library like the SOAP server for UPNP would also be affected.
I found ... | Crashes in HTTP server found with fuzzing | https://api.github.com/repos/cybergarage/mupnp/issues/21/comments | 1 | 2023-12-28T21:05:35Z | 2023-12-30T04:36:23Z | https://github.com/cybergarage/mupnp/issues/21 | 2,058,820,284 | 21 | 5,865 |
CVE-2023-7152 | 2023-12-29T05:15:09.473 | A vulnerability, which was classified as critical, has been found in MicroPython 1.21.0/1.22.0-preview. Affected by this issue is the function poll_set_add_fd of the file extmod/modselect.c. The manipulation leads to use after free. The exploit has been disclosed to the public and may be used. The patch is identified a... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "ADJACENT_NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.2,
"confidentialityImpact... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch"
],
"url": "https://github.com/jimmo/micropython/commit/8b24aa36ba978eafc6114b6798b47b7bfecdca26"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/micropython/microp... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:micropython:micropython:1.21.0:*:*:*:*:*:*:*",
"matchCriteriaId": "92240FCD-0BA9-46D0-9C9A-2CDD8FE2A769",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"416"
] | 416 | https://github.com/micropython/micropython/issues/12887 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"micropython",
"micropython"
] | ## Environment
- **OS**: Ubuntu 22.04 64bit
- **Version**: micropython at commit db06041d59ef8d5524340c4d2c4490c8e770591f
- **Build**: unix standard build
- **Bug Type**: use-after-free
- **Bug location**: `micropython/extmod/modselect.c:151`
- **Detection Tool**: our custom tool, not disclosed yet
- **Credits... | Use After Free at modselect.c:151 | https://api.github.com/repos/micropython/micropython/issues/12887/comments | 3 | 2023-11-05T09:58:40Z | 2023-12-21T03:52:51Z | https://github.com/micropython/micropython/issues/12887 | 1,977,696,903 | 12,887 | 5,866 |
CVE-2023-7158 | 2023-12-29T07:15:11.060 | A vulnerability was found in MicroPython up to 1.21.0. It has been classified as critical. Affected is the function slice_indices of the file objslice.c. The manipulation leads to heap-based buffer overflow. It is possible to launch the attack remotely. The exploit has been disclosed to the public and may be used. Upgr... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/micropython/micropython/issues/13007"
},
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/micropython/micropython/pull/13039"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:micropython:micropython:*:*:*:*:*:*:*:*",
"matchCriteriaId": "98250EF6-59E9-440F-95EB-5A5BB2B54639",
"versionEndExcluding": "1.22.0",
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/micropython/micropython/issues/13007 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"micropython",
"micropython"
] | # Summary
- **OS**: Ubuntu 22.04
- **version**: micropython@a00c9d56db775ee5fc14c2db60eb07bab8e872dd
- **port**: unix
- **contribution**: Junwha Hong and Wonil Jang @S2-Lab, UNIST
- **description**: `slice_indices` misinterpret float value as integer value, and leads to buffer overflow.
# PoC
```c
# A cla... | heap-buffer-overflow: mis-interpretation of float as int at slice_indices | https://api.github.com/repos/micropython/micropython/issues/13007/comments | 2 | 2023-11-17T09:50:54Z | 2023-11-22T06:11:45Z | https://github.com/micropython/micropython/issues/13007 | 1,998,711,622 | 13,007 | 5,867 |
CVE-2023-7080 | 2023-12-29T12:15:47.970 | The V8 inspector intentionally allows arbitrary code execution within the Workers sandbox for debugging. wrangler dev would previously start an inspector server listening on all network interfaces. This would allow an attacker on the local network to connect to the inspector and run arbitrary code. Additionally, the in... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "ADJACENT_NETWORK",
"availabilityImpact": "NONE",
"baseScore": 8.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
... | [
{
"source": "cna@cloudflare.com",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/cloudflare/workers-sdk/issues/4430"
},
{
"source": "cna@cloudflare.com",
"tags": [
"Patch"
],
"url": "https://github.com/cloudflare/workers-sdk/pull/4437"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cloudflare:wrangler:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "9BC3CE33-76AB-4812-BCBD-C65F5728471D",
"versionEndExcluding": "2.20.2",
"versionEndIncluding": null,
"versionS... | [
"269"
] | 269 | https://github.com/cloudflare/workers-sdk/issues/4430 | [
"Issue Tracking",
"Patch"
] | github.com | [
"cloudflare",
"workers-sdk"
] | ### Which Cloudflare product(s) does this pertain to?
Wrangler core
### What version(s) of the tool(s) are you using?
3.15.0
### What version of Node are you using?
21.1.0
### What operating system are you using?
Mac
### Describe the Bug
When running `wrangler dev`, a lot of services are list... | 🐛 BUG: Wrangler is still listening on the wildcard address even with --ip localhost | https://api.github.com/repos/cloudflare/workers-sdk/issues/4430/comments | 1 | 2023-11-12T12:57:30Z | 2024-04-10T04:39:32Z | https://github.com/cloudflare/workers-sdk/issues/4430 | 1,989,391,363 | 4,430 | 5,868 |
CVE-2023-50570 | 2023-12-29T15:15:09.927 | An issue in the component IPAddressBitsDivision of IPAddress v5.1.0 leads to an infinite loop. This is disputed because an infinite loop occurs only for cases in which the developer supplies invalid arguments. The product is not intended to always halt for contrived inputs. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/seancfoley/IPAddress/issues/118"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:seancfoley:ipaddress:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "0087B5A8-11C3-4AE2-9D43-FEE2C5CBE156",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"835"
] | 835 | https://github.com/seancfoley/IPAddress/issues/118 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"seancfoley",
"IPAddress"
] | IPAddress version: 5.1.0
I have these code that can't finished in time:
```java
public void equalsFuzzerTest() {
try {
long tempLong = 5979084832330744063L;
int tempInt = -1;
IPAddressBitsDivision iPAddressBitsDivision = new IPAddressBitsDivision(tempLong, tempLong... | new IPAddressBitsDivision leads to infinite loop | https://api.github.com/repos/seancfoley/IPAddress/issues/118/comments | 12 | 2023-12-05T09:23:22Z | 2024-01-29T18:54:43Z | https://github.com/seancfoley/IPAddress/issues/118 | 2,025,738,205 | 118 | 5,869 |
CVE-2023-50572 | 2023-12-29T15:15:10.030 | An issue in the component GroovyEngine.execute of jline-groovy v3.24.1 allows attackers to cause an OOM (OutofMemory) error. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/jline/jline3/issues/909"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/jline/jline... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jline:jline:3.24.1:*:*:*:*:*:*:*",
"matchCriteriaId": "6E44BBF7-0E0D-4F52-94DD-5F4D1A5833B9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"787"
] | 787 | https://github.com/jline/jline3/issues/909 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"jline",
"jline3"
] | version: 3.24.1
Reproduced code:
```java
public void executeFuzzerTest() {
try {
GroovyEngine groovyEngine = new GroovyEngine();
Object result = groovyEngine.execute("/\n/*777777777777777777777777777777");
} catch (Exception e) {
}
}
``` | GroovyEngine.execute cause an OOM exception | https://api.github.com/repos/jline/jline3/issues/909/comments | 3 | 2023-12-07T03:41:36Z | 2024-01-18T12:12:48Z | https://github.com/jline/jline3/issues/909 | 2,029,822,844 | 909 | 5,870 |
CVE-2023-50069 | 2023-12-29T21:15:08.713 | WireMock with GUI versions 3.2.0.0 through 3.0.4.0 are vulnerable to stored cross-site scripting (SXSS) through the recording feature. An attacker can host a malicious payload and perform a test mapping pointing to the attacker's file, and the result will render on the Matched page in the Body area, resulting in the ex... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/holomekc/wiremock/issues/51"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wiremock:wiremock:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C1A72A41-BF60-4FB0-8E43-810DB8735B17",
"versionEndExcluding": null,
"versionEndIncluding": "3.2.0",
"versionStartExclu... | [
"79"
] | 79 | https://github.com/holomekc/wiremock/issues/51 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"holomekc",
"wiremock"
] | ## Summary
WireMock with GUI versions `3.2.0.0` through `3.0.4.0` are vulnerable to stored cross-site scripting (SXSS) through the recording feature. An attacker can host a malicious payload and perform a test mapping pointing to the attacker's file, and the result will render on the `Matched` page in the `Body` area,... | Security Vulnerability - Stored Cross Site Scripting | https://api.github.com/repos/holomekc/wiremock/issues/51/comments | 4 | 2023-12-19T17:36:07Z | 2023-12-27T10:00:42Z | https://github.com/holomekc/wiremock/issues/51 | 2,049,137,735 | 51 | 5,871 |
CVE-2023-52263 | 2023-12-30T19:15:08.253 | Brave Browser before 1.59.40 does not properly restrict the schema for WebUI factory and redirect. This is related to browser/brave_content_browser_client.cc and browser/ui/webui/brave_web_ui_controller_factory.cc. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/brave/brave-browser/issues/32449"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/brave/brave-browser/issues/32... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:brave:browser:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DA80DCA2-44C6-45ED-BED6-A34F25D2A86D",
"versionEndExcluding": "1.59.40",
"versionEndIncluding": null,
"versionStartExcludi... | [
"601"
] | 601 | https://github.com/brave/brave-browser/issues/32449 | [
"Issue Tracking",
"Patch"
] | github.com | [
"brave",
"brave-browser"
] | ## Description
Follow up to https://github.com/brave/brave-browser/issues/32425
for STR see https://bravesoftware.slack.com/archives/C7VLGSR55/p1692737541055759?thread_ts=1692642768.785349&cid=C7VLGSR55
| [hackerone] browser crash 2 | https://api.github.com/repos/brave/brave-browser/issues/32449/comments | 6 | 2023-08-22T21:09:39Z | 2023-08-23T16:20:32Z | https://github.com/brave/brave-browser/issues/32449 | 1,862,212,493 | 32,449 | 5,872 |
CVE-2023-52263 | 2023-12-30T19:15:08.253 | Brave Browser before 1.59.40 does not properly restrict the schema for WebUI factory and redirect. This is related to browser/brave_content_browser_client.cc and browser/ui/webui/brave_web_ui_controller_factory.cc. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/brave/brave-browser/issues/32449"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/brave/brave-browser/issues/32... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:brave:browser:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DA80DCA2-44C6-45ED-BED6-A34F25D2A86D",
"versionEndExcluding": "1.59.40",
"versionEndIncluding": null,
"versionStartExcludi... | [
"601"
] | 601 | https://github.com/brave/brave-browser/issues/32473 | [
"Issue Tracking",
"Patch"
] | github.com | [
"brave",
"brave-browser"
] | ###Release Notes
- [hackerone] browser crash. ([#32425](https://github.com/brave/brave-browser/issues/32425))
- [hackerone] browser crash 2. ([#32449](https://github.com/brave/brave-browser/issues/32449))
- Upgrade from Chromium 116.0.5845.96 to Chromium 116.0.5845.114. ([#32451](https://github.com/brave/brave-... | Desktop Release Notes for 1.57.x Release #4 | https://api.github.com/repos/brave/brave-browser/issues/32473/comments | 0 | 2023-08-23T14:35:09Z | 2023-08-23T18:12:05Z | https://github.com/brave/brave-browser/issues/32473 | 1,863,468,219 | 32,473 | 5,873 |
CVE-2023-52266 | 2023-12-31T00:15:44.440 | ehttp 1.0.6 before 17405b9 has an epoll_socket.cpp read_func use-after-free. An attacker can make many connections over a short time to trigger this. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/hongliuliao/ehttp/commit/17405b975948abc216f6a085d2d027ec1cfd5766"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/hongliuliao/ehttp/issues/38"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hongliuliao:ehttp:1.0.6:*:*:*:*:*:*:*",
"matchCriteriaId": "9DE98FAE-2E96-4FDF-8B5F-3544877A28B5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"416"
] | 416 | https://github.com/hongliuliao/ehttp/issues/38 | [
"Exploit"
] | github.com | [
"hongliuliao",
"ehttp"
] | Hi!
When executing my fuzz tests I discovered a few bugs at the following locations:
* Out-of-bounds-read in void _log at simple_log.cpp:221
* Use-after-free in read_func(void*) at epoll_socket.cpp:234
## Out-of-bounds-read in void _log at simple_log.cpp:221 when sending a malformed HTTP method, large url, or... | Memory Corruption Bugs | https://api.github.com/repos/hongliuliao/ehttp/issues/38/comments | 2 | 2023-10-08T01:27:38Z | 2023-10-08T22:13:28Z | https://github.com/hongliuliao/ehttp/issues/38 | 1,931,587,083 | 38 | 5,874 |
CVE-2021-46900 | 2023-12-31T05:15:08.040 | Sympa before 6.2.62 relies on a cookie parameter for certain security objectives, but does not ensure that this parameter exists and has an unpredictable value. Specifically, the cookie parameter is both a salt for stored passwords and an XSS protection mechanism. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Mitigation",
"Vendor Advisory"
],
"url": "https://github.com/sympa-community/sympa-community.github.io/blob/master/security/2021-001.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Mitigation",
"Vendor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sympa:sympa:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9A9DE075-6416-41D9-972D-872DCA7E20AE",
"versionEndExcluding": "6.2.62",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"327"
] | 327 | https://github.com/sympa-community/sympa/issues/1091 | [
"Issue Tracking",
"Mitigation",
"Vendor Advisory"
] | github.com | [
"sympa-community",
"sympa"
] | <!--- ↑↑ Provide a general summary of the issue in the Title above ↑↑ -->
Expected Behavior
-----------------
`cookie` parameter will be obsoleted.
Possible Solution
-----------------
<!--- Not obligatory, but suggest ideas how to implement the addition or change -->
- [x] Modify codes that are using cooki... | [CVE-2021-46900] Obsolete `cookie` parameter that is not secure enough | https://api.github.com/repos/sympa-community/sympa/issues/1091/comments | 21 | 2021-01-21T01:24:47Z | 2023-12-31T11:11:12Z | https://github.com/sympa-community/sympa/issues/1091 | 790,588,544 | 1,091 | 5,875 |
CVE-2023-52284 | 2023-12-31T06:15:08.487 | Bytecode Alliance wasm-micro-runtime (aka WebAssembly Micro Runtime or WAMR) before 1.3.0 can have an "double free or corruption" error for a valid WebAssembly module because push_pop_frame_ref_offset is mishandled. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/bytecodealliance/wasm-micro-runtime/compare/WAMR-1.2.3...WAMR-1.3.0"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bytecodealliance:webassembly_micro_runtime:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8D76C425-15E0-42A8-B9E2-8EC56FF15980",
"versionEndExcluding": "1.3.0",
"versionEndIncluding": null,
... | [
"415"
] | 415 | https://github.com/bytecodealliance/wasm-micro-runtime/issues/2586 | [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
] | github.com | [
"bytecodealliance",
"wasm-micro-runtime"
] | ## Describe the Bug
When executing a valid WebAssembly module using the `iwasm`, the program terminates with a "double free or corruption" error, probably originating from the `wasm_loader_ctx_destroy` function in `wasm_loader.c`.
`iwasm --version`: iwasm 1.2.3
`uname -a`: Linux node0.wamr.randtest-pg0.utah.cl... | Double Free or Corruption Error on Valid WebAssembly Module Load | https://api.github.com/repos/bytecodealliance/wasm-micro-runtime/issues/2586/comments | 2 | 2023-09-22T23:14:32Z | 2023-10-18T02:47:47Z | https://github.com/bytecodealliance/wasm-micro-runtime/issues/2586 | 1,909,611,567 | 2,586 | 5,876 |
CVE-2021-46901 | 2023-12-31T07:15:07.443 | examples/6lbr/apps/6lbr-webserver/httpd.c in CETIC-6LBR (aka 6lbr) 1.5.0 has a strcat stack-based buffer overflow via a request for a long URL over a 6LoWPAN network. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/cetic/6lbr/blob/c3092a1ccc6b6b0e668f33f6f4b2d6967975d664/examples/6lbr/apps/6lbr-webserver/httpd.c#L119"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Adv... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:cetic:cetic-6lbr:1.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "E465E0D8-8E05-4C5D-B4FD-CE7B5AFC5E46",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"787"
] | 787 | https://github.com/cetic/6lbr/issues/414 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"cetic",
"6lbr"
] | if u enter url like this:
[bbbb::100]/AAAAAAAAAAAAAAAAA.....AAAAAAAA (len = 1000)
it will crash with stack smashing.
because of strcat - https://github.com/cetic/6lbr/blob/develop/examples/6lbr/apps/6lbr-webserver/httpd.c#L119 | webserver buffer overflow when processing requested url | https://api.github.com/repos/cetic/6lbr/issues/414/comments | 10 | 2021-05-27T10:06:47Z | 2023-12-31T10:57:08Z | https://github.com/cetic/6lbr/issues/414 | 903,503,461 | 414 | 5,877 |
CVE-2023-26157 | 2024-01-02T05:15:08.160 | Versions of the package libredwg before 0.12.5.6384 are vulnerable to Denial of Service (DoS) due to an out-of-bounds read involving section->num_pages in decode_r2007.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "report@snyk.io",
"tags": [
"Patch"
],
"url": "https://github.com/LibreDWG/libredwg/commit/c8cf03ce4c2315b146caf582ea061c0460193bcc"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/L... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C0D7618D-9F7C-4654-822E-48A907537B85",
"versionEndExcluding": "0.12.5.6384",
"versionEndIncluding": null,
"versionStartExcl... | [
"125"
] | 125 | https://github.com/LibreDWG/libredwg/issues/850 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi rurban,
Making a quick report on an out-of-bounds read fuzzing crash. I confirmed this with a build using the `--enable-release` flag as well.
Release build error:
```
./programs/dwgread crash.dwg
ERROR: Invalid num_pages 7274598, skip
ERROR: Invalid section->pages[0] size
Warning: Failed to find secti... | Out-of-Bound Read in read_data_section in 0.12.5 | https://api.github.com/repos/LibreDWG/libredwg/issues/850/comments | 1 | 2023-09-26T13:28:46Z | 2023-10-30T17:06:23Z | https://github.com/LibreDWG/libredwg/issues/850 | 1,913,517,983 | 850 | 5,878 |
CVE-2023-26159 | 2024-01-02T05:15:08.630 | Versions of the package follow-redirects before 1.15.4 are vulnerable to Improper Input Validation due to the improper handling of URLs by the url.parse() function. When new URL() throws an error, it can be manipulated to misinterpret the hostname. An attacker could exploit this weakness to redirect traffic to a malici... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 7.3,
"baseSeverity": "HIGH",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/follow-redirects/follow-redirects/issues/235"
},
{
"source": "report@snyk.io",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/follow-redire... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:follow-redirects:follow_redirects:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "5E9B14E8-F184-4F4C-8275-8FE1D093D258",
"versionEndExcluding": "1.15.4",
"versionEndIncluding": null,
... | [
"601"
] | 601 | https://github.com/follow-redirects/follow-redirects/issues/235 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"follow-redirects",
"follow-redirects"
] | By the way, I read about Security.md but huntr.dev service has changed to AL/ML open source bugbounty platform. So I couldn't report it to there. Because of that reason, I'm writing it here.
# Description
Below is part of `follow-redirects`'s `index.js` code.
```
function urlToOptions(urlObject) {
var options ... | [Security Report] hostname spoofing via url.parse in follow-redirects | https://api.github.com/repos/follow-redirects/follow-redirects/issues/235/comments | 5 | 2023-12-29T04:41:20Z | 2023-12-30T17:57:18Z | https://github.com/follow-redirects/follow-redirects/issues/235 | 2,059,059,047 | 235 | 5,879 |
CVE-2023-50019 | 2024-01-02T22:15:09.147 | An issue was discovered in open5gs v2.6.6. InitialUEMessage, Registration request sent at a specific time can crash AMF due to incorrect error handling of Nudm_UECM_Registration response. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 5.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"int... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/open5gs/open5gs/commit/7278714133422cee46c32c7523f81ec2cecad9e2"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:open5gs:open5gs:2.6.6:*:*:*:*:*:*:*",
"matchCriteriaId": "27AA61AC-D4A0-40B4-8965-E578FC5F8D03",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"755"
] | 755 | https://github.com/open5gs/open5gs/issues/2733 | [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
] | github.com | [
"open5gs",
"open5gs"
] | ### Open5GS Release, Revision, or Tag
v2.6.6
### Steps to reproduce
### Bug Description
According to page 143 of 3GPP TS 23.502 V18.3.0 (2023-09), in steps 14a-c of the User Equipment (UE) registration process, if the UE's registration type is initial registration or emergency registration, the AMF will send ... | [Bug]: InitialUEMessage, Registration request sent at a specific time can crash AMF due to incorrect error handling in the gmm state machine | https://api.github.com/repos/open5gs/open5gs/issues/2733/comments | 3 | 2023-11-13T08:21:42Z | 2024-01-03T22:31:43Z | https://github.com/open5gs/open5gs/issues/2733 | 1,990,113,647 | 2,733 | 5,880 |
CVE-2023-50020 | 2024-01-02T22:15:09.190 | An issue was discovered in open5gs v2.6.6. SIGPIPE can be used to crash AMF. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/open5gs/open5gs/commit/1aba814938e3a1b2eec7014bf6ce132d34622e08"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:open5gs:open5gs:2.6.6:*:*:*:*:*:*:*",
"matchCriteriaId": "27AA61AC-D4A0-40B4-8965-E578FC5F8D03",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"400"
] | 400 | https://github.com/open5gs/open5gs/issues/2734 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"open5gs",
"open5gs"
] | ### Open5GS Release, Revision, or Tag
v2.6.6
### Steps to reproduce
Please set up the environment following the instructions at [https://github.com/s5uishida/open5gs_5gc_ueransim_sample_config](https://github.com/open5gs/open5gs/issues/url), we use just one UE and one UPF.
Run the following script on the UE for a... | [Bug]: AMF crashed on SIGPIPE | https://api.github.com/repos/open5gs/open5gs/issues/2734/comments | 5 | 2023-11-13T09:19:51Z | 2023-12-28T22:31:41Z | https://github.com/open5gs/open5gs/issues/2734 | 1,990,219,100 | 2,734 | 5,881 |
CVE-2023-49551 | 2024-01-02T23:15:12.233 | An issue in Cesanta mjs 2.20.0 allows a remote attacker to cause a denial of service via the mjs_op_json_parse function in the msj.c file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/cesanta/mjs/issues/257"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:2.20.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CF8D39F6-ACB1-46F8-87CF-1B41EFC157BE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"20"
] | 20 | https://github.com/cesanta/mjs/issues/257 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"cesanta",
"mjs"
] | **The name of an affected Product**
[mjs](https://github.com/cesanta/mjs)
**The affected version**
Commit: [b1b6eac](https://github.com/cesanta/mjs/commit/b1b6eac6b1e5b830a5cb14f8f4dc690ef3162551) (Tag: [2.20.0](https://github.com/cesanta/mjs/releases/tag/2.20.0))
**Description**
An issue in cesanta mjs 2.20.0... | SEGV in mjs_op_json_parse() at mjs.c:11364 | https://api.github.com/repos/cesanta/mjs/issues/257/comments | 0 | 2023-11-26T09:51:38Z | 2023-12-22T02:39:20Z | https://github.com/cesanta/mjs/issues/257 | 2,010,974,674 | 257 | 5,882 |
CVE-2023-49552 | 2024-01-02T23:15:12.290 | An Out of Bounds Write in Cesanta mjs 2.20.0 allows a remote attacker to cause a denial of service via the mjs_op_json_stringify function in the msj.c file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/cesanta/mjs/issues/256"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:2.20.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CF8D39F6-ACB1-46F8-87CF-1B41EFC157BE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"125"
] | 125 | https://github.com/cesanta/mjs/issues/256 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"cesanta",
"mjs"
] | **The name of an affected Product**
[mjs](https://github.com/cesanta/mjs)
**The affected version**
Commit: [b1b6eac](https://github.com/cesanta/mjs/commit/b1b6eac6b1e5b830a5cb14f8f4dc690ef3162551) (Tag: [2.20.0](https://github.com/cesanta/mjs/releases/tag/2.20.0))
**Description**
An issue in cesanta mjs 2.20.0... | stack-overflow in mjs_op_json_stringify() at mjs.c:11362 | https://api.github.com/repos/cesanta/mjs/issues/256/comments | 0 | 2023-11-26T08:00:13Z | 2023-12-22T02:21:04Z | https://github.com/cesanta/mjs/issues/256 | 2,010,943,506 | 256 | 5,883 |
CVE-2023-49554 | 2024-01-03T00:15:08.987 | Use After Free vulnerability in YASM 1.3.0.86.g9def allows a remote attacker to cause a denial of service via the do_directive function in the modules/preprocs/nasm/nasm-pp.c component. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/yasm/yasm/issues/249"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yasm_project:yasm:1.3.0.86.g9def:*:*:*:*:*:*:*",
"matchCriteriaId": "C9D63BD2-36F6-440B-AC78-6F48EDDC12CD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"416"
] | 416 | https://github.com/yasm/yasm/issues/249 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"yasm",
"yasm"
] | **The name of an affected Product**
[yasm](https://github.com/yasm/yasm)
**The affected version**
Commit: [9defefa](https://github.com/yasm/yasm/commit/9defefae9fbcb6958cddbfa778c1ea8605da8b8b)
yasm 1.3.0.86.g9def
**Description**
An issue in yasm 1.3.0.86.g9def allows a attacker to cause a denial of service v... | heap-use-after-free in the function do_directive() at modules/preprocs/nasm/nasm-pp.c:2389 | https://api.github.com/repos/yasm/yasm/issues/249/comments | 0 | 2023-11-20T14:16:57Z | 2024-01-03T11:22:46Z | https://github.com/yasm/yasm/issues/249 | 2,002,305,193 | 249 | 5,884 |
CVE-2024-21907 | 2024-01-03T16:15:08.793 | Newtonsoft.Json before version 13.0.1 is affected by a mishandling of exceptional conditions vulnerability. Crafted data that is passed to the JsonConvert.DeserializeObject method may trigger a StackOverflow exception resulting in denial of service. Depending on the usage of the library, an unauthenticated and remote a... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "disclosure@vulncheck.com",
"tags": [
"Exploit"
],
"url": "https://alephsecurity.com/2018/10/22/StackOverflowException/"
},
{
"source": "disclosure@vulncheck.com",
"tags": [
"Exploit"
],
"url": "https://alephsecurity.com/vulns/aleph-2018004"
},
{
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:newtonsoft:json.net:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F7713CE4-2B29-46C2-8416-75B9F3C258F6",
"versionEndExcluding": "13.0.1",
"versionEndIncluding": null,
"versionStartEx... | [
"755"
] | 755 | https://github.com/JamesNK/Newtonsoft.Json/issues/2457 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"JamesNK",
"Newtonsoft.Json"
] | We're using [BlackDuck](https://www.blackducksoftware.com) to scan our projects and recently Newtonsoft.Json was flagged as a medium security risk (BDSA-2018-5195) because of the following issue:
> Newtonsoft.Json is vulnerable to denial-of-service (DoS) due to a stack overflow that can occur whenever nested objects... | ALEPH-2018004 - DOS vulnerability | https://api.github.com/repos/JamesNK/Newtonsoft.Json/issues/2457/comments | 4 | 2021-01-19T07:17:50Z | 2025-05-20T17:43:40Z | https://github.com/JamesNK/Newtonsoft.Json/issues/2457 | 788,773,605 | 2,457 | 5,885 |
CVE-2024-21910 | 2024-01-03T16:15:09.090 | TinyMCE versions before 5.10.0 are affected by a cross-site scripting vulnerability. A remote and unauthenticated attacker could introduce crafted image or link URLs that would result in the execution of arbitrary JavaScript in an editing user's browser.
| {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "disclosure@vulncheck.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/advisories/GHSA-r8hm-w5f7-wj39"
},
{
"source": "disclosure@vulncheck.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tiny:tinymce:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1CDEC000-8A31-496B-9137-F71208146F9D",
"versionEndExcluding": "5.10.0",
"versionEndIncluding": null,
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/jazzband/django-tinymce/issues/366 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jazzband",
"django-tinymce"
] | Fixed in 5.6.0 https://github.com/tinymce/tinymce/security/advisories/GHSA-w7jx-j77m-wp65
Fixed in 5.7.1 https://github.com/tinymce/tinymce/security/advisories/GHSA-5vm8-hhgr-jcjp | Upgrade TinyMCE to fix Cross-site scripting vulnerabilities | https://api.github.com/repos/jazzband/django-tinymce/issues/366/comments | 4 | 2021-08-23T11:08:05Z | 2021-11-26T03:08:27Z | https://github.com/jazzband/django-tinymce/issues/366 | 976,911,068 | 366 | 5,886 |
CVE-2023-50630 | 2024-01-04T08:15:09.053 | Cross Site Scripting (XSS) vulnerability in xiweicheng TMS v.2.28.0 allows a remote attacker to execute arbitrary code via a crafted script to the click here function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/xiweicheng/tms/issues/19"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/xiweicheng... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:teamwork_management_system_project:teamwork_management_system:2.28.0:*:*:*:*:*:*:*",
"matchCriteriaId": "DE8ABD88-819F-4ED4-92B8-23A9A515596B",
"versionEndExcluding": null,
"versionEndIn... | [
"79"
] | 79 | https://github.com/xiweicheng/tms/issues/19 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"xiweicheng",
"tms"
] | [Suggested description]
I found many cross site scripting(XSS) vulnerabilities exists in tms (markdown XSS). Every edit or comment page with markdown may has this vulnerability. It's too many to list.
[Vulnerability Type]
Cross Site Scripting (XSS)
[Vendor of Product]
https://github.com/xiweicheng/tms
[Affe... | There are cross site scripting vulnerabilities exist in tms | https://api.github.com/repos/xiweicheng/tms/issues/19/comments | 0 | 2023-12-08T01:00:38Z | 2023-12-16T02:40:51Z | https://github.com/xiweicheng/tms/issues/19 | 2,031,753,380 | 19 | 5,887 |
CVE-2024-22047 | 2024-01-04T21:15:09.720 | A race condition exists in Audited 4.0.0 to 5.3.3 that can result in an authenticated user to cause audit log entries to be attributed to another user.
| {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 3.1,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "disclosure@vulncheck.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/advisories/GHSA-hjp3-5g2q-7jww"
},
{
"source": "disclosure@vulncheck.com",
"tags": [
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:collectiveidea:audited:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6F9F98EC-034A-4BD6-85FF-038B75CC82BF",
"versionEndExcluding": "5.3.3",
"versionEndIncluding": null,
"versionStart... | [
"362"
] | 362 | https://github.com/collectiveidea/audited/issues/601 | [
"Issue Tracking",
"Patch",
"Vendor Advisory"
] | github.com | [
"collectiveidea",
"audited"
] | Hello,
We are using the audit to generate around 20 thousand records daily. In some cases we find that the user who performed the action is incorrect. Analyzing the code we saw that the Thread.current[:audited_store] method is called to get the current user. We use AWS with loadbalancer with 2 to 4 servers at peak h... | Incorrect User in Audit | https://api.github.com/repos/collectiveidea/audited/issues/601/comments | 6 | 2021-11-01T14:07:05Z | 2023-05-04T09:15:07Z | https://github.com/collectiveidea/audited/issues/601 | 1,041,214,509 | 601 | 5,888 |
CVE-2024-22086 | 2024-01-05T04:15:07.833 | handle_request in http.c in cherry through 4b877df has an sscanf stack-based buffer overflow via a long URI, leading to remote code execution. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
],
"url": "https://github.com/hayyp/cherry/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hayyp:cherry:*:*:*:*:*:*:*:*",
"matchCriteriaId": "70E7BB44-A376-4183-A41D-775D68B6A751",
"versionEndExcluding": null,
"versionEndIncluding": "2021-01-05",
"versionStartExclu... | [
"787"
] | 787 | https://github.com/hayyp/cherry/issues/1 | [
"Exploit",
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
] | github.com | [
"hayyp",
"cherry"
] | Hi!
I discovered a remote stack buffer overflow vulnerability in the function handle_request() at http.c, line 54:
https://github.com/hayyp/cherry/blob/4b877df82f9bccd2384c58ee9145deaab94de4ba/src/http.c#L54
Any project that utilizes cherry is vulnerable to remote code execution. I have outlined the reproduct... | Remote Stack Buffer Overflow (Potential Code Execution) | https://api.github.com/repos/hayyp/cherry/issues/1/comments | 0 | 2024-01-03T23:31:25Z | 2024-01-03T23:31:25Z | https://github.com/hayyp/cherry/issues/1 | 2,064,781,262 | 1 | 5,889 |
CVE-2024-22087 | 2024-01-05T04:15:07.880 | route in main.c in Pico HTTP Server in C through f3b69a6 has an sprintf stack-based buffer overflow via a long URI, leading to remote code execution. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
],
"url": "https://github.com/foxweb/pico/issues/31"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:alekseykurepin:pico_http_server_in_c:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8FEF2CA7-7D88-42A8-A7B2-4CDA320AD91E",
"versionEndExcluding": null,
"versionEndIncluding": "2021-04-02",
... | [
"787"
] | 787 | https://github.com/foxweb/pico/issues/31 | [
"Exploit",
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
] | github.com | [
"foxweb",
"pico"
] | Hi!
I discovered a remote stack buffer overflow vulnerability in the function void route() at main.c, line 81:
https://github.com/foxweb/pico/blob/f3b69a65d7f8cd1ab0ecb027ae6d02881e8d83f7/main.c#L79-L81
Any project that utilizes pico is vulnerable to remote code execution. I have outlined the reproduction ste... | Remote buffer overflow in main.c | https://api.github.com/repos/foxweb/pico/issues/31/comments | 1 | 2024-01-03T18:18:40Z | 2024-01-26T08:04:40Z | https://github.com/foxweb/pico/issues/31 | 2,064,459,091 | 31 | 5,890 |
CVE-2024-22088 | 2024-01-05T04:15:07.930 | Lotos WebServer through 0.1.1 (commit 3eb36cc) has a use-after-free in buffer_avail() at buffer.h via a long URI, because realloc is mishandled. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Mitigation",
"Vendor Advisory"
],
"url": "https://github.com/chendotjs/lotos/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chendotjs:lotos_webserver:*:*:*:*:*:*:*:*",
"matchCriteriaId": "17684EB2-E7FE-41D8-A4B2-70A0F26FB24D",
"versionEndExcluding": null,
"versionEndIncluding": "0.1.1",
"versionSt... | [
"416"
] | 416 | https://github.com/chendotjs/lotos/issues/7 | [
"Exploit",
"Issue Tracking",
"Mitigation",
"Vendor Advisory"
] | github.com | [
"chendotjs",
"lotos"
] | Hi!
After executing my fuzz tests I discovered a remote use-after-free vulnerability in static inline size_t buffer_avail(const buffer_t *pb) at buffer.h, line 25:
https://github.com/chendotjs/lotos/blob/3eb36cc3723a1dc9bb737505f0c8a3538ee16347/src/buffer.h#L25
Any project that utilizes lotos (including the ex... | Use-After-Free in buffer_avail() through version 0.1.1 (commit 3eb36cc) | https://api.github.com/repos/chendotjs/lotos/issues/7/comments | 0 | 2023-12-28T21:49:07Z | 2023-12-28T21:49:07Z | https://github.com/chendotjs/lotos/issues/7 | 2,058,846,456 | 7 | 5,891 |
CVE-2023-7215 | 2024-01-08T02:15:14.027 | A vulnerability, which was classified as problematic, has been found in Chanzhaoyu chatgpt-web 2.11.1. This issue affects some unknown processing. The manipulation of the argument Description with the input <image src onerror=prompt(document.domain)> leads to cross site scripting. The attack may be initiated remotely. ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/Chanzhaoyu/chatgpt-web/issues/2001"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory",
"VDB Entry"
],
"url": "http... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chanzhaoyu:chatgpt_web:2.11.1:*:*:*:*:*:*:*",
"matchCriteriaId": "743F26DA-3A55-47CD-8FA3-F22DF98A9EFC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/Chanzhaoyu/chatgpt-web/issues/2001 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"Chanzhaoyu",
"chatgpt-web"
] | # Security Alert: XSS Vulnerability Discovered in Description Parameter
🚨 I've identified a critical security issue in our application. This concerns a Cross-Site Scripting (XSS) vulnerability found in the Description parameter. It's crucial we address this to prevent unauthorized access and potential harm.
##... | Vulnerability : Stored Xss on Description parameter | https://api.github.com/repos/Chanzhaoyu/chatgpt-web/issues/2001/comments | 2 | 2023-12-21T23:40:35Z | 2024-01-05T01:45:55Z | https://github.com/Chanzhaoyu/chatgpt-web/issues/2001 | 2,053,178,132 | 2,001 | 5,892 |
CVE-2024-21663 | 2024-01-09T00:15:44.790 | Discord-Recon is a Discord bot created to automate bug bounty recon, automated scans and information gathering via a discord server. Discord-Recon is vulnerable to remote code execution. An attacker is able to execute shell commands in the server without having an admin role. This vulnerability has been fixed in versio... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.9,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/DEMON1A/Discord-Recon/commit/f9cb0f67177f5e2f1022295ca8e641e47837ec7a"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:demon1a:discord-recon:*:*:*:*:*:discord:*:*",
"matchCriteriaId": "C89EDC32-6EF6-4868-A4A5-911E552F82B8",
"versionEndExcluding": "0.0.8",
"versionEndIncluding": null,
"version... | [
"77"
] | 77 | https://github.com/DEMON1A/Discord-Recon/issues/23 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"DEMON1A",
"Discord-Recon"
] | ## Summary
The prips command in the Discord Recon project is vulnerable to command injection. It lacks proper input sanitization, allowing potential attackers to execute arbitrary commands through user input, which is then passed to the subprocess.Popen function.
Screenshot of vulnerable code
 via a crafted MP4 file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/gpac/gpac/issues/2698"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/gpac/gpac/iss... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3:dev:*:*:*:*:*:*",
"matchCriteriaId": "0099B624-674B-4F45-9270-DD638617A1D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"835"
] | 835 | https://github.com/gpac/gpac/issues/2698 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"gpac",
"gpac"
] | 1.Version
MP4Box - GPAC version 2.3-DEV-rev636-gfbd7e13aa-master
(c) 2000-2023 Telecom Paris distributed under LGPL v2.1+ - https://gpac.io
Please cite our work in your research:
GPAC Filters: https://doi.org/10.1145/3339825.3394929
GPAC: https://doi.org/10.1145/1291233.1291452
GPAC Configuration: --static-... | Infinite loop in av1_uvlc media_tools/av_parsers.c:1664 | https://api.github.com/repos/gpac/gpac/issues/2698/comments | 1 | 2023-12-01T04:51:55Z | 2023-12-01T10:00:42Z | https://github.com/gpac/gpac/issues/2698 | 2,020,058,777 | 2,698 | 5,894 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.