cve_id stringlengths 13 16 | cve_published stringlengths 23 23 | cve_descriptions stringlengths 54 997 | cve_metrics dict | cve_references listlengths 1 68 | cve_configurations listlengths 1 5 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 76
values | url stringlengths 37 79 | cve_tags listlengths 1 4 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 3 88.6k ⌀ | issue_title stringlengths 3 335 | issue_comments_url stringlengths 56 81 | issue_comments_count int64 0 146 | issue_created_at stringlengths 20 20 | issue_updated_at stringlengths 20 20 | issue_html_url stringlengths 37 62 | issue_github_id int64 128M 2.84B | issue_number int64 1 128k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2022-35105 | 2022-08-16T21:15:11.107 | SWFTools commit 772e55a2 was discovered to contain a heap-buffer overflow via /bin/png2swf+0x552cea. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/183"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:-:*:*:*:*:*:*:*",
"matchCriteriaId": "05E27E60-6223-457B-BF90-E747C9C5DEE1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"787"
] | 787 | https://github.com/matthiaskramm/swftools/issues/183 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | Hi, I currently learn to use fuzz tech to detect bugs and I found something in this repo.
in order to reproduce the crash info, please attach ASAN when you compile this repo.
## heap buffer overflow
### reproduce
command to reproduce the crash : ./png2swf -j 50 [sample file] -o /dev/null
### sample file
[id... | bug found in swftools-png2swf | https://api.github.com/repos/swftools/swftools/issues/183/comments | 0 | 2022-07-03T08:51:23Z | 2022-07-04T03:22:44Z | https://github.com/swftools/swftools/issues/183 | 1,292,247,150 | 183 |
CVE-2022-35107 | 2022-08-16T21:15:11.180 | SWFTools commit 772e55a2 was discovered to contain a stack overflow via vfprintf at /stdio-common/vfprintf.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/184"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:-:*:*:*:*:*:*:*",
"matchCriteriaId": "05E27E60-6223-457B-BF90-E747C9C5DEE1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"770"
] | 770 | https://github.com/matthiaskramm/swftools/issues/184 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | # heap buffer overflow
### reproduce
command to reproduce: ./pdf2swf -G -f -t [sample file] -o /dev/null
### sample file
[id458_heap_overflow_draw_stroke.zip](https://github.com/matthiaskramm/swftools/files/9036118/id458_heap_overflow_draw_stroke.zip)
### crash info
```
==11942==ERROR: AddressSanitizer: heap-b... | bug report swftools-pdf2swf | https://api.github.com/repos/swftools/swftools/issues/184/comments | 0 | 2022-07-04T03:13:51Z | 2022-07-04T03:20:37Z | https://github.com/swftools/swftools/issues/184 | 1,292,557,716 | 184 |
CVE-2022-35113 | 2022-08-16T21:15:11.363 | SWFTools commit 772e55a2 was discovered to contain a heap-buffer overflow via swf_DefineLosslessBitsTagToImage at /modules/swfbits.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/185"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:-:*:*:*:*:*:*:*",
"matchCriteriaId": "05E27E60-6223-457B-BF90-E747C9C5DEE1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"787"
] | 787 | https://github.com/matthiaskramm/swftools/issues/185 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | # swfrender
## heap buffer overflow
### command to reproduce
`./swfrender [sample file] -o /dev/null`
### crash sample
[id8_heap-buffer-overflow_swf_DefineLosslessBitsTagToImage.zip](https://github.com/matthiaskramm/swftools/files/9036326/id8_heap-buffer-overflow_swf_DefineLosslessBitsTagToImage.zip)
### cr... | bug found in swfrender | https://api.github.com/repos/swftools/swftools/issues/185/comments | 0 | 2022-07-04T04:15:24Z | 2022-07-04T04:15:24Z | https://github.com/swftools/swftools/issues/185 | 1,292,592,670 | 185 |
CVE-2022-36186 | 2022-08-17T15:15:08.480 | A Null Pointer dereference vulnerability exists in GPAC 2.1-DEV-revUNKNOWN-master via the function gf_filter_pid_set_property_full () at filter_core/filter_pid.c:5250,which causes a Denial of Service (DoS). This vulnerability was fixed in commit b43f9d1. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2223"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.1:dev:*:*:*:*:*:*",
"matchCriteriaId": "2963671B-FA29-45DB-80B0-92F9E55F5159",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/2223 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [ ] I looked for a similar issue and couldn't find any.
- [ ] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ ] I give enough info... | A NULL pointer dereference in gf_filter_pid_set_property_full | https://api.github.com/repos/gpac/gpac/issues/2223/comments | 0 | 2022-07-07T10:26:55Z | 2022-07-12T17:13:11Z | https://github.com/gpac/gpac/issues/2223 | 1,297,164,642 | 2,223 |
CVE-2022-36190 | 2022-08-17T15:15:08.543 | GPAC mp4box 2.1-DEV-revUNKNOWN-master has a use-after-free vulnerability in function gf_isom_dovi_config_get. This vulnerability was fixed in commit fef6242. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2220"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"416"
] | 416 | https://github.com/gpac/gpac/issues/2220 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [ ] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Heap Use After Free in function gf_isom_dovi_config_get | https://api.github.com/repos/gpac/gpac/issues/2220/comments | 1 | 2022-07-06T03:36:02Z | 2022-07-12T17:13:50Z | https://github.com/gpac/gpac/issues/2220 | 1,295,074,577 | 2,220 |
CVE-2022-36191 | 2022-08-17T16:15:07.920 | A heap-buffer-overflow had occurred in function gf_isom_dovi_config_get of isomedia/avc_ext.c:2490, as demonstrated by MP4Box. This vulnerability was fixed in commit fef6242. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2218"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2218 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [ ] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | heap-buffer-overflow in function gf_isom_dovi_config_get | https://api.github.com/repos/gpac/gpac/issues/2218/comments | 0 | 2022-07-04T10:10:00Z | 2022-07-12T17:13:10Z | https://github.com/gpac/gpac/issues/2218 | 1,292,941,893 | 2,218 |
CVE-2022-35164 | 2022-08-18T05:15:07.603 | LibreDWG v0.12.4.4608 & commit f2dea29 was discovered to contain a heap use-after-free via bit_copy_chain. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/497"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0A8152A2-6867-4B31-8F47-A1A655A49EFF",
"versionEndExcluding": "0.12.4.4608",
"versionEndIncluding": null,
"versionStartExcl... | [
"416"
] | 416 | https://github.com/LibreDWG/libredwg/issues/497 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | # Vulnerability description
version: [0.12.4.4608](https://github.com/LibreDWG/libredwg/releases/tag/0.12.4.4608) & latest commit [f2dea29](https://github.com/LibreDWG/libredwg/commit/f2dea296a0a3bb16afdae8d2ca16749a617a4383)
poc: [poc](https://github.com/0xdd96/PoC/raw/main/libredwg/UAF-bit_copy_chain)
command: ./... | Heap use-after-free still exists in the bit_copy_chain | https://api.github.com/repos/LibreDWG/libredwg/issues/497/comments | 2 | 2022-06-17T12:04:26Z | 2023-06-27T10:19:27Z | https://github.com/LibreDWG/libredwg/issues/497 | 1,274,949,181 | 497 |
CVE-2022-35165 | 2022-08-18T05:15:07.657 | An issue in AP4_SgpdAtom::AP4_SgpdAtom() of Bento4-1.6.0-639 allows attackers to cause a Denial of Service (DoS) via a crafted mp4 input. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/712"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"835"
] | 835 | https://github.com/axiomatic-systems/Bento4/issues/712 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # Vulnerability description
**version:** Bento4-1.6.0-639
**command:** ./mp42aac $POC /dev/null
**Download:** [poc](https://github.com/0xdd96/PoC/raw/main/Bento4/AP4_SgpdAtom::AP4_SgpdAtom-out-of-memory)
Here is the trace reported by ASAN:
```
$ mp42aac poc /dev/null
AddressSanitizer: Out of memory. The proc... | Possible memory exhuastion in AP4_SgpdAtom::AP4_SgpdAtom(). The process has exhausted 65536MB memory. | https://api.github.com/repos/axiomatic-systems/Bento4/issues/712/comments | 0 | 2022-05-31T14:44:43Z | 2022-06-04T17:16:23Z | https://github.com/axiomatic-systems/Bento4/issues/712 | 1,253,977,287 | 712 |
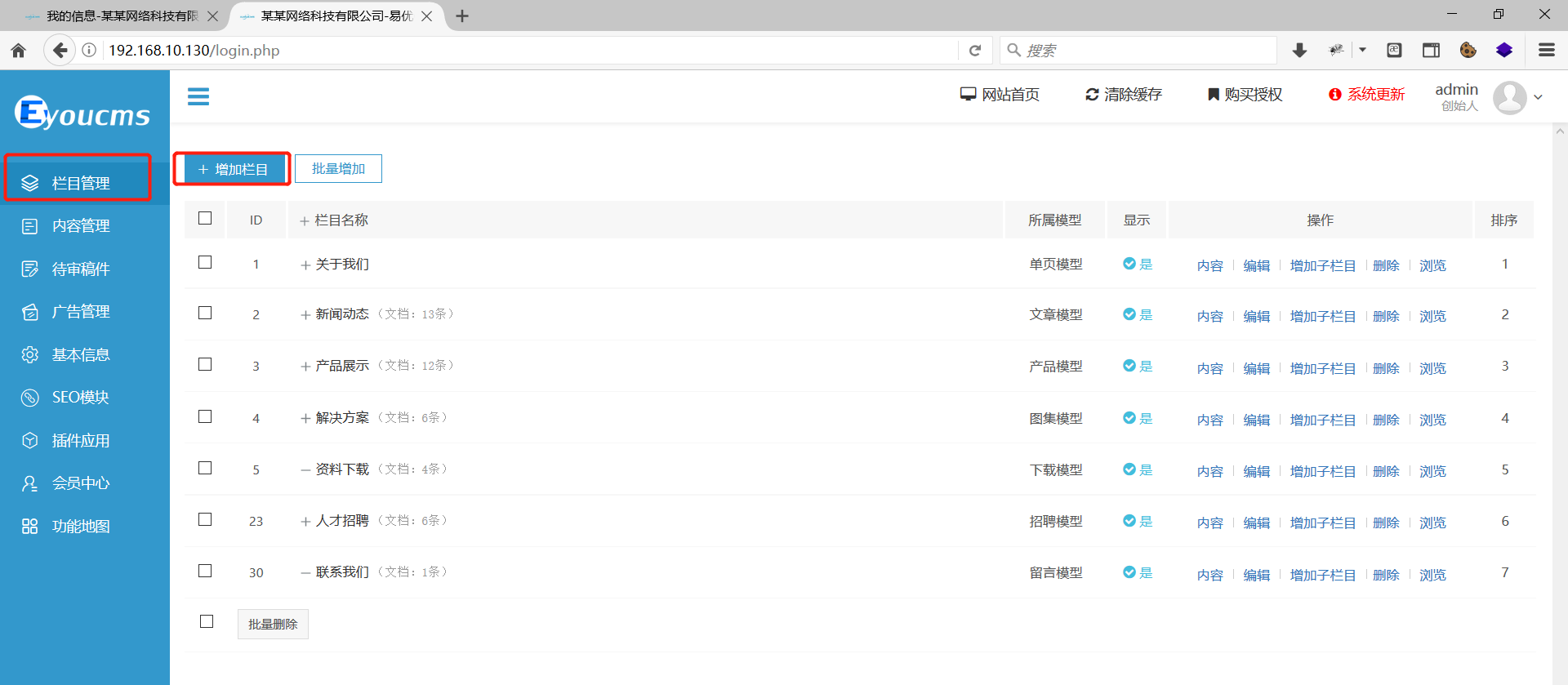
CVE-2022-36225 | 2022-08-19T17:15:07.897 | EyouCMS V1.5.8-UTF8-SP1 is vulnerable to Cross Site Request Forgery (CSRF) via the background, column management function and add. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/26"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.5.8:*:*:*:*:*:*:*",
"matchCriteriaId": "82E421EB-ECC8-42A4-8384-4187474D1AC3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"352"
] | 352 | https://github.com/weng-xianhu/eyoucms/issues/26 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | version:V1.5.8-UTF8-SP1

In the background, column management function and add.
Add test data... | EyouCMS v1.5.8 has a vulnerability, Cross-site request forgery(CSRF) | https://api.github.com/repos/weng-xianhu/eyoucms/issues/26/comments | 2 | 2022-07-17T13:08:03Z | 2023-02-28T08:54:23Z | https://github.com/weng-xianhu/eyoucms/issues/26 | 1,307,093,003 | 26 |
CVE-2021-3574 | 2022-08-26T16:15:08.943 | A vulnerability was found in ImageMagick-7.0.11-5, where executing a crafted file with the convert command, ASAN detects memory leaks. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "LOW",
"baseScore": 3.3,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integrityI... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ImageMagick/ImageMagick/commit/c6ad94fbb7b280f39c2fbbdc1c140e51b1b466e9"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.11-5:*:*:*:*:*:*:*",
"matchCriteriaId": "3769F997-3EBC-4222-B3D4-8709A7AA49FE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/3540 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
I have written a descriptive issue title
I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to ensure it has not already been reported
I have verified that I am using the latest ... | AddressSanitizer report LeakSanitizer: detected memory leaks when executing convert command | https://api.github.com/repos/ImageMagick/ImageMagick/issues/3540/comments | 11 | 2021-04-13T14:50:19Z | 2022-11-30T17:19:10Z | https://github.com/ImageMagick/ImageMagick/issues/3540 | 857,040,605 | 3,540 |
CVE-2022-0284 | 2022-08-29T15:15:09.183 | A heap-based-buffer-over-read flaw was found in ImageMagick's GetPixelAlpha() function of 'pixel-accessor.h'. This vulnerability is triggered when an attacker passes a specially crafted Tagged Image File Format (TIFF) image to convert it into a PICON file format. This issue can potentially lead to a denial of service a... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2022-0284"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "90A073A6-900F-44EE-B29F-05CB65058078",
"versionEndExcluding": "7.1.0-20",
"versionEndIncluding": null,
"versionS... | [
"125"
] | 125 | https://github.com/ImageMagick/ImageMagick/issues/4729 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### ImageMagick version
7.1.0-20
### Operating system
Linux
### Operating system, version and so on
Linux ubuntu 5.4.0-73-generic #82~18.04.1-Ubuntu SMP Fri Apr 16 15:10:02 UTC 2021 x86_64 x86_64 x86_64 GNU/Linux
### Description
Hi, ImageMagick security team
This is ZhangJiaxing (@r0fm1a) from Codesafe Team of ... | Heap Buffer Overflow | https://api.github.com/repos/ImageMagick/ImageMagick/issues/4729/comments | 4 | 2022-01-19T07:07:49Z | 2022-02-19T13:35:53Z | https://github.com/ImageMagick/ImageMagick/issues/4729 | 1,107,736,894 | 4,729 |
CVE-2022-1115 | 2022-08-29T15:15:10.297 | A heap-buffer-overflow flaw was found in ImageMagick’s PushShortPixel() function of quantum-private.h file. This vulnerability is triggered when an attacker passes a specially crafted TIFF image file to ImageMagick for conversion, potentially leading to a denial of service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2022-1115"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "62ED872E-70D8-4736-9876-F307A77839D4",
"versionEndExcluding": "6.9.12-44",
"versionEndIncluding": null,
"version... | [
"787"
] | 787 | https://github.com/ImageMagick/ImageMagick/issues/4974 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### ImageMagick version
7.1.0-28
### Operating system
Linux
### Operating system, version and so on
OS: Ubuntu 20.04.3 LTS
Version: ImageMagick 7.1.0-28 Q16-HDRI x86_64 2022-03-04 https://imagemagick.org
Copyright: (C) 1999 ImageMagick Studio LLC
License: https://imagemagick.org/script/license.php ... | heap-buffer-overflow in magick at quantum-private.h PushShortPixel | https://api.github.com/repos/ImageMagick/ImageMagick/issues/4974/comments | 1 | 2022-03-22T02:10:38Z | 2022-03-24T01:28:05Z | https://github.com/ImageMagick/ImageMagick/issues/4974 | 1,176,173,021 | 4,974 |
CVE-2022-36749 | 2022-08-30T22:15:09.630 | RPi-Jukebox-RFID v2.3.0 was discovered to contain a command injection vulnerability via the component /htdocs/utils/Files.php. This vulnerability is exploited via a crafted payload injected into the file name of an uploaded file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/MiczFlor/RPi-Jukebox-RFID/issues/1859"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Adv... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sourcefabric:rpi-jukebox-rfid:2.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D564CC8A-AFE5-48C3-910C-08BDEF93FBEA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"vers... | [
"78"
] | 78 | https://github.com/MiczFlor/RPi-Jukebox-RFID/issues/1859 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"MiczFlor",
"RPi-Jukebox-RFID"
] | Hello,
I would like to report for possible vulnerability.
In file https://github.com/MiczFlor/RPi-Jukebox-RFID/blob/develop/htdocs/trackEdit.php
```php
//line 136
if(isset($_GET['folder']) && $_GET['folder'] != "") {
$post['folder'] = $_GET['folder'];
} else {
if(isset($_POST['folder']) && $_POST... | 🐛 | Command Injection and XSS vulnerabilities reports | https://api.github.com/repos/MiczFlor/RPi-Jukebox-RFID/issues/1859/comments | 4 | 2022-07-18T14:10:45Z | 2024-09-15T09:50:33Z | https://github.com/MiczFlor/RPi-Jukebox-RFID/issues/1859 | 1,308,022,012 | 1,859 |
CVE-2022-38530 | 2022-09-06T23:15:09.010 | GPAC v2.1-DEV-rev232-gfcaa01ebb-master was discovered to contain a stack overflow when processing ISOM_IOD. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2216"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2216 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | **version info:**
```
root:# MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev232-gfcaa01ebb-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your research:
GPAC Filters: https://doi.org/10.1145/3339825.3394929
GPAC: https://doi.org/10.114... | AddressSanitizer: stack-overflow when processing ISOM_IOD | https://api.github.com/repos/gpac/gpac/issues/2216/comments | 0 | 2022-07-02T17:45:58Z | 2022-07-12T17:13:10Z | https://github.com/gpac/gpac/issues/2216 | 1,292,105,535 | 2,216 |
CVE-2020-10735 | 2022-09-09T14:15:08.660 | A flaw was found in python. In algorithms with quadratic time complexity using non-binary bases, when using int("text"), a system could take 50ms to parse an int string with 100,000 digits and 5s for 1,000,000 digits (float, decimal, int.from_bytes(), and int() for binary bases 2, 4, 8, 16, and 32 are not affected). Th... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2022/09/21/1"
},
{
"source": "secalert@redhat.com",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/list... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:python:python:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0743C1B3-D44D-4940-AAF4-25DEFB46AC74",
"versionEndExcluding": "3.7.14",
"versionEndIncluding": null,
"versionStartExcludin... | [
"704"
] | 704 | https://github.com/python/cpython/issues/95778 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"python",
"cpython"
] | ## Problem
A Denial Of Service (DoS) issue was identified in CPython because we use binary bignum’s for our `int` implementation. A huge integer will always consume a near-quadratic amount of CPU time in conversion to or from a base 10 (decimal) string with a large number of digits. No efficient algorithm exists to ... | CVE-2020-10735: Prevent DoS by large int<->str conversions | https://api.github.com/repos/python/cpython/issues/95778/comments | 24 | 2022-08-08T07:53:39Z | 2023-02-07T04:35:46Z | https://github.com/python/cpython/issues/95778 | 1,331,477,062 | 95,778 |
CVE-2022-40438 | 2022-09-14T21:15:10.627 | Buffer overflow vulnerability in function AP4_MemoryByteStream::WritePartial in mp42aac in Bento4 v1.6.0-639, allows attackers to cause a denial of service via a crafted file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/751"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"120"
] | 120 | https://github.com/axiomatic-systems/Bento4/issues/751 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, developers of Bento4:
In the test of the binary mp42aac instrumented with ASAN. There are some inputs causing heap-buffer-overflow. Here is the ASAN mode output:
=================================================================
==4695==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x6190000027a0 at ... | Heap-buffer-overflow with ASAN in mp42aac | https://api.github.com/repos/axiomatic-systems/Bento4/issues/751/comments | 0 | 2022-09-07T02:21:29Z | 2022-09-18T23:10:27Z | https://github.com/axiomatic-systems/Bento4/issues/751 | 1,364,000,633 | 751 |
CVE-2022-40439 | 2022-09-14T21:15:10.670 | An memory leak issue was discovered in AP4_StdcFileByteStream::Create in mp42ts in Bento4 v1.6.0-639, allows attackers to cause a denial of service via a crafted file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/750"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"401"
] | 401 | https://github.com/axiomatic-systems/Bento4/issues/750 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, developers of Bento4:
In the test of the binary mp42ts instrumented with ASAN. There are some inputs causing memory leaks. Here is the ASAN mode output:
=================================================================
==18321==ERROR: LeakSanitizer: detected memory leaks
Direct leak of 48 byte(s) in 1 objec... | Memory leaks with ASAN in mp42ts | https://api.github.com/repos/axiomatic-systems/Bento4/issues/750/comments | 0 | 2022-09-06T14:00:13Z | 2023-05-29T02:53:17Z | https://github.com/axiomatic-systems/Bento4/issues/750 | 1,363,336,565 | 750 |
CVE-2022-40737 | 2022-09-15T04:15:24.610 | An issue was discovered in Bento4 through 1.6.0-639. A buffer over-read exists in the function AP4_StdcFileByteStream::WritePartial located in System/StdC/Ap4StdCFileByteStream.cpp, called from AP4_ByteStream::Write and AP4_HdlrAtom::WriteFields. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/756"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "180AEBD6-AF89-4F0F-856E-D8B977C762C0",
"versionEndExcluding": null,
"versionEndIncluding": "1.6.0-639",
"versionStartExcl... | [
"125"
] | 125 | https://github.com/axiomatic-systems/Bento4/issues/756 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hello, I use fuzzer to test bianry mp4split, and found some vulnerabilities,the following is the details.
# Bug1
```
root@c511e4bf49bc:/mp4split/mp4split# ./mp4split FishFuzz/crashes/id:000000,sig:06,src:000011,op:flip1,pos:31240,1216870
=================================================================
==258946... | there are some vulnerabilities in binary mp4split | https://api.github.com/repos/axiomatic-systems/Bento4/issues/756/comments | 2 | 2022-09-14T11:20:27Z | 2023-06-26T06:40:26Z | https://github.com/axiomatic-systems/Bento4/issues/756 | 1,372,814,057 | 756 |
CVE-2022-40774 | 2022-09-18T19:15:09.277 | An issue was discovered in Bento4 through 1.6.0-639. There is a NULL pointer dereference in AP4_StszAtom::GetSampleSize. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/757"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "180AEBD6-AF89-4F0F-856E-D8B977C762C0",
"versionEndExcluding": null,
"versionEndIncluding": "1.6.0-639",
"versionStartExcl... | [
"476"
] | 476 | https://github.com/axiomatic-systems/Bento4/issues/757 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi There,
I tested the binary mp42ts with my fuzzer, and a crash incurred, i.e., SEGV on an unknown address error. Here are the details:
```
AddressSanitizer:DEADLYSIGNAL
=================================================================
==6287==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x... | SEGV at AP4_StszAtom::GetSampleSize(unsigned int, unsigned int&) in binary mp42ts | https://api.github.com/repos/axiomatic-systems/Bento4/issues/757/comments | 2 | 2022-09-17T03:04:47Z | 2023-06-26T09:40:27Z | https://github.com/axiomatic-systems/Bento4/issues/757 | 1,376,646,543 | 757 |
CVE-2022-40775 | 2022-09-18T19:15:09.323 | An issue was discovered in Bento4 through 1.6.0-639. A NULL pointer dereference occurs in AP4_StszAtom::WriteFields. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/758"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "180AEBD6-AF89-4F0F-856E-D8B977C762C0",
"versionEndExcluding": null,
"versionEndIncluding": "1.6.0-639",
"versionStartExcl... | [
"476"
] | 476 | https://github.com/axiomatic-systems/Bento4/issues/758 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi there, I use my fuzzer for fuzzing the binary mp4decrypt, and this binary crashes with the following:
```
AddressSanitizer:DEADLYSIGNAL
=================================================================
==24087==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x000000702ee8 bp 0x7ffcf40a75f0 s... | SEGV error | https://api.github.com/repos/axiomatic-systems/Bento4/issues/758/comments | 0 | 2022-09-17T06:02:37Z | 2023-06-26T09:41:06Z | https://github.com/axiomatic-systems/Bento4/issues/758 | 1,376,678,566 | 758 |
CVE-2022-40008 | 2022-09-20T20:15:10.510 | SWFTools commit 772e55a was discovered to contain a heap-buffer overflow via the function readU8 at /lib/ttf.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/188"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:2021-12-16:*:*:*:*:*:*:*",
"matchCriteriaId": "BB9D1BB0-75D0-4C0B-8297-540D6A24F722",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"787"
] | 787 | https://github.com/matthiaskramm/swftools/issues/188 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | system info
Ubuntu x86_64, clang 10.0, ttftool (latest master https://github.com/matthiaskramm/swftools/commit/772e55a271f66818b06c6e8c9b839befa51248f4)
Command line
./src/ttftool poc
```
=================================================================
==26368==ERROR: AddressSanitizer: heap-buffer-overflow on ... | heap-buffer-overflow exists in the function readU8 in lib/ttf.c | https://api.github.com/repos/swftools/swftools/issues/188/comments | 0 | 2022-07-28T08:51:57Z | 2022-07-28T08:59:46Z | https://github.com/swftools/swftools/issues/188 | 1,320,609,012 | 188 |
CVE-2022-40009 | 2022-09-20T20:15:10.550 | SWFTools commit 772e55a was discovered to contain a heap-use-after-free via the function grow_unicode at /lib/ttf.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/190"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:2021-12-16:*:*:*:*:*:*:*",
"matchCriteriaId": "BB9D1BB0-75D0-4C0B-8297-540D6A24F722",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"416"
] | 416 | https://github.com/matthiaskramm/swftools/issues/190 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | system info
Ubuntu x86_64, clang 10.0, ttftool (latest master https://github.com/matthiaskramm/swftools/commit/772e55a271f66818b06c6e8c9b839befa51248f4)
Command line
./src/ttftool poc
```
=================================================================
==26408==ERROR: AddressSanitizer: heap-use-after-free on a... | heap-use-after-free exists in the function grow_unicode in /lib/ttf.c | https://api.github.com/repos/swftools/swftools/issues/190/comments | 0 | 2022-07-28T08:56:02Z | 2022-07-28T08:59:20Z | https://github.com/swftools/swftools/issues/190 | 1,320,614,087 | 190 |
CVE-2022-35085 | 2022-09-21T00:15:10.207 | SWFTools commit 772e55a2 was discovered to contain a memory leak via /lib/mem.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Cvjark/Poc/blob/main/swftools/gif2swf/CVE-2022-35085.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:-:*:*:*:*:*:*:*",
"matchCriteriaId": "05E27E60-6223-457B-BF90-E747C9C5DEE1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"401"
] | 401 | https://github.com/matthiaskramm/swftools/issues/181 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | Hi, I currently learn to use fuzz tech to detect bugs and I found something in this repo.
in order to reproduce the crash info, please attach ASAN when you compile this repo.
# gif2swf
## heap-buffer-overflow
### reproduce
please use command : `./gif2swf -o /dev/null [sample file]` to reproduce the cras... | bug found in swftools-gif2swf | https://api.github.com/repos/swftools/swftools/issues/181/comments | 0 | 2022-07-03T08:28:59Z | 2022-07-04T03:28:11Z | https://github.com/swftools/swftools/issues/181 | 1,292,243,070 | 181 |
CVE-2022-40929 | 2022-09-28T18:15:09.813 | XXL-JOB 2.2.0 has a Command execution vulnerability in background tasks. NOTE: this is disputed because the issues/4929 report is about an intended and supported use case (running arbitrary Bash scripts on behalf of users). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/xuxueli/xxl-job/issues/2979"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xuxueli:xxl-job:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "C7AE69F1-6781-47B8-933D-989F4EF5ED19",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"78"
] | 78 | https://github.com/xuxueli/xxl-job/issues/2979 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"xuxueli",
"xxl-job"
] | 后台任务存在命令执行漏洞
### Which version of XXL-JOB do you using?
XXL-JOB 2.2.0
---
### 利用流程
#### 新建任务
<img width="899" alt="截屏2022-09-13 下午7 26 54" src="https://user-images.githubusercontent.com/72059221/189889779-75d361a8-0edf-4c24-803d-8cbd40709df2.png">
#### 选择IDE 编辑
<img width="148" alt="截屏2022-09-13 下午7 27... | 后台任务存在命令执行漏洞 | https://api.github.com/repos/xuxueli/xxl-job/issues/2979/comments | 1 | 2022-09-13T11:30:39Z | 2024-11-10T06:59:10Z | https://github.com/xuxueli/xxl-job/issues/2979 | 1,371,299,019 | 2,979 |
CVE-2022-41841 | 2022-09-30T05:15:11.260 | An issue was discovered in Bento4 through 1.6.0-639. A NULL pointer dereference occurs in AP4_File::ParseStream in Core/Ap4File.cpp, which is called from AP4_File::AP4_File. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/779"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "180AEBD6-AF89-4F0F-856E-D8B977C762C0",
"versionEndExcluding": null,
"versionEndIncluding": "1.6.0-639",
"versionStartExcl... | [
"476"
] | 476 | https://github.com/axiomatic-systems/Bento4/issues/779 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hello, I use my fuzzer to fuzz binary mp4tag and binary mp42hevc , and found some crashes. The bug1 is different from issue #295, because i run the test-001.mp4 finding it useless. Here are the details.
# Bug1
```
┌──(kali㉿kali)-[~/Desktop/Bento4/cmakebuild]
└─$ ./mp4tag mp4tag_poc ... | There are some vulnerabilities in Bento4 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/779/comments | 0 | 2022-09-27T08:01:55Z | 2023-06-26T06:51:17Z | https://github.com/axiomatic-systems/Bento4/issues/779 | 1,387,303,483 | 779 |
CVE-2022-41845 | 2022-09-30T05:15:11.787 | An issue was discovered in Bento4 1.6.0-639. There ie excessive memory consumption in the function AP4_Array<AP4_ElstEntry>::EnsureCapacity in Core/Ap4Array.h. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/747"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"770"
] | 770 | https://github.com/axiomatic-systems/Bento4/issues/747 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, i find 3 out-of-memory errors in Bento4. I saved all my test files [here](https://github.com/WorldExecute/files/tree/main/Bento4)
Here are the details.
For **mp4audioclip** with [test input](https://github.com/WorldExecute/files/tree/main/Bento4/mp4audioclip/out-of-memory):
```
test_1:
====================... | out-of-memory | https://api.github.com/repos/axiomatic-systems/Bento4/issues/747/comments | 0 | 2022-08-28T07:58:44Z | 2023-05-29T02:53:16Z | https://github.com/axiomatic-systems/Bento4/issues/747 | 1,353,278,230 | 747 |
CVE-2022-41845 | 2022-09-30T05:15:11.787 | An issue was discovered in Bento4 1.6.0-639. There ie excessive memory consumption in the function AP4_Array<AP4_ElstEntry>::EnsureCapacity in Core/Ap4Array.h. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/747"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"770"
] | 770 | https://github.com/axiomatic-systems/Bento4/issues/770 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # Summary
Hello, I use my fuzzer to fuzz binary mp4tag , the three binary all crashede, and shows that allocator is out of memory trying to allocate 0xxxxxxx bytes. Then I use the crash input to test binary mpesplit and mp42hevc,and all crashed beacuse of same situation. The version of Bento4 is the latest commit[5b7c... | there are some vulnerabilities in binary mp4tag | https://api.github.com/repos/axiomatic-systems/Bento4/issues/770/comments | 0 | 2022-09-23T07:02:26Z | 2023-06-26T06:33:03Z | https://github.com/axiomatic-systems/Bento4/issues/770 | 1,383,377,290 | 770 |
CVE-2022-41846 | 2022-09-30T05:15:11.870 | An issue was discovered in Bento4 1.6.0-639. There ie excessive memory consumption in the function AP4_DataBuffer::ReallocateBuffer in Core/Ap4DataBuffer.cpp. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/342"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"770"
] | 770 | https://github.com/axiomatic-systems/Bento4/issues/342 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | A crafted input will lead to Memory allocation failed in Ap4DataBuffer.cpp at Bento4 1.5.1-627
Triggered by
./mp42hls crash2.mp4
Poc
[crash2.zip](https://github.com/axiomatic-systems/Bento4/files/2685099/crash2.zip)
Bento4 Version 1.5.1-627
The ASAN information is as follows:
```
==92387==ERROR: AddressSa... | Allocate for large amounts of memory failed in Ap4DataBuffer.cpp:210 at Bento4 1.5.1-627 when running mp42hls | https://api.github.com/repos/axiomatic-systems/Bento4/issues/342/comments | 1 | 2018-12-17T08:48:55Z | 2019-01-12T20:15:42Z | https://github.com/axiomatic-systems/Bento4/issues/342 | 391,610,142 | 342 |
CVE-2022-41847 | 2022-09-30T05:15:11.957 | An issue was discovered in Bento4 1.6.0-639. A memory leak exists in AP4_StdcFileByteStream::Create(AP4_FileByteStream*, char const*, AP4_FileByteStream::Mode, AP4_ByteStream*&) in System/StdC/Ap4StdCFileByteStream.cpp. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/750"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"401"
] | 401 | https://github.com/axiomatic-systems/Bento4/issues/759 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | I use AFL when fuzzing and got some crashes.
=================================================================
==3780==ERROR: LeakSanitizer: detected memory leaks
Direct leak of 48 byte(s) in 1 object(s) allocated from:
#0 0x4c470d in operator new(unsigned long) (/home/hjsz/Bento4/cmakebuild/mp4fragment+0x4c4... | There are memory leaks in mp4fragment | https://api.github.com/repos/axiomatic-systems/Bento4/issues/759/comments | 0 | 2022-09-17T08:19:32Z | 2023-05-29T02:53:19Z | https://github.com/axiomatic-systems/Bento4/issues/759 | 1,376,705,591 | 759 |
CVE-2022-41847 | 2022-09-30T05:15:11.957 | An issue was discovered in Bento4 1.6.0-639. A memory leak exists in AP4_StdcFileByteStream::Create(AP4_FileByteStream*, char const*, AP4_FileByteStream::Mode, AP4_ByteStream*&) in System/StdC/Ap4StdCFileByteStream.cpp. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/750"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"401"
] | 401 | https://github.com/axiomatic-systems/Bento4/issues/775 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hello, I use fuzer to test binary acc2mp4, and found some carshes, which can result binary mp4split crash too. Here are the details.
# Bug1
```
root@d5f4647d38bd:/aac2mp4/aac2mp4# /Bento4/build/aac2mp4 crash1 /dev/null
AAC frame [000000]: size = -7, 96000 kHz, 0 ch
=================================================... | there are some bugs in Bento4 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/775/comments | 0 | 2022-09-24T07:42:46Z | 2023-06-26T06:38:57Z | https://github.com/axiomatic-systems/Bento4/issues/775 | 1,384,568,694 | 775 |
CVE-2022-41419 | 2022-10-03T14:15:22.013 | Bento4 v1.6.0-639 was discovered to contain a memory leak via the AP4_Processor::Process function in the mp4encrypt binary. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/766"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"401"
] | 401 | https://github.com/axiomatic-systems/Bento4/issues/766 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # Summary
Hi, developers of Bento4:
I tested the binary mp4encrypt, and a crash incurred, i.e., memory leaks error. The version of Bento4 is the latest (the newest master branch) and the operation system is Ubuntu 18.04.6 LTS (docker). The following is the details.
# Details
```
root@c08635047aea:/fuzz-mp4encryp... | Detected memory leaks in mp4encrypt | https://api.github.com/repos/axiomatic-systems/Bento4/issues/766/comments | 0 | 2022-09-20T01:45:02Z | 2023-06-26T05:57:20Z | https://github.com/axiomatic-systems/Bento4/issues/766 | 1,378,706,570 | 766 |
CVE-2022-41424 | 2022-10-03T14:15:23.097 | Bento4 v1.6.0-639 was discovered to contain a memory leak via the AP4_SttsAtom::Create function in mp42hls. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/768"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"401"
] | 401 | https://github.com/axiomatic-systems/Bento4/issues/768 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # Summary
Hi there, I tested the binary mp42hls, the version of Bento4 is the latest (the newest master branch) and the operation system is Ubuntu 18.04.6 LTS (docker) and this binary crash with the following.
# Details
```
root@2e47aa8b3277:/test_mp42hls# ./mp42hls --audio-track-id 2 ./mp42hls\-poc\-1
ERROR: ... | Detected memory leaks in mp42hls | https://api.github.com/repos/axiomatic-systems/Bento4/issues/768/comments | 0 | 2022-09-21T16:36:04Z | 2023-06-26T05:25:33Z | https://github.com/axiomatic-systems/Bento4/issues/768 | 1,381,208,895 | 768 |
CVE-2022-41428 | 2022-10-03T14:15:24.697 | Bento4 v1.6.0-639 was discovered to contain a heap overflow via the AP4_BitReader::ReadBits function in mp4mux. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/773"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/axiomatic-systems/Bento4/issues/773 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # Summary
Hello, I found three heap buffer overflow bugs in AP4_Atom::TypeFromString(char const*), AP4_BitReader::ReadBit() and AP4_BitReader::ReadBits(unsigned int). They come from mp4tag and mp4mux, respectively.
# Bug1
Heap-buffer-overflow on address 0x602000000332 in mp4tag:
```
root@728d9sls452:/fuzz-mp... | Some heap-buffer-overflow bugs in Bento4 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/773/comments | 0 | 2022-09-23T16:44:03Z | 2023-06-12T07:07:50Z | https://github.com/axiomatic-systems/Bento4/issues/773 | 1,384,054,185 | 773 |
CVE-2022-41500 | 2022-10-18T23:15:09.380 | EyouCMS V1.5.9 was discovered to contain multiple Cross-Site Request Forgery (CSRF) vulnerabilities via the Members Center, Editorial Membership, and Points Recharge components. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/27#issue-1410014422"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracki... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.5.9:*:*:*:*:*:*:*",
"matchCriteriaId": "42A15197-E862-429C-8ECB-79D0B850C9C5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"352"
] | 352 | https://github.com/weng-xianhu/eyoucms/issues/27#issue-1410014422 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | A security vulnerability exists in EyouCMS V1.5.9 in the backend, Members Center, Editing Membership, and Points Top-up.
1. Enter the background - > member center - > edit member - > points recharge, as shown in the figure:
 | https://api.github.com/repos/weng-xianhu/eyoucms/issues/27/comments | 1 | 2022-10-15T02:26:03Z | 2023-02-28T02:38:51Z | https://github.com/weng-xianhu/eyoucms/issues/27 | 1,410,014,422 | 27 |
CVE-2022-43032 | 2022-10-19T14:15:09.853 | An issue was discovered in Bento4 v1.6.0-639. There is a memory leak in AP4_DescriptorFactory::CreateDescriptorFromStream in Core/Ap4DescriptorFactory.cpp, as demonstrated by mp42aac. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/763"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"401"
] | 401 | https://github.com/axiomatic-systems/Bento4/issues/763 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, developers of Bento4:
In the test of the binary mp42aac instrumented with ASAN. There are some inputs causing memory leaks. Here is the ASAN mode output:
=================================================================
==19530==ERROR: LeakSanitizer: detected memory leaks
Direct leak of 80 byte(s) in 1 obje... | Memory leaks with ASAN in mp42aac | https://api.github.com/repos/axiomatic-systems/Bento4/issues/763/comments | 0 | 2022-09-19T06:18:05Z | 2022-09-19T06:18:05Z | https://github.com/axiomatic-systems/Bento4/issues/763 | 1,377,456,877 | 763 |
CVE-2022-43033 | 2022-10-19T14:15:09.897 | An issue was discovered in Bento4 1.6.0-639. There is a bad free in the component AP4_HdlrAtom::~AP4_HdlrAtom() which allows attackers to cause a Denial of Service (DoS) via a crafted input. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/765"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"416"
] | 416 | https://github.com/axiomatic-systems/Bento4/issues/765 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, developers of Bento4:
In the test of the binary mp42aac instrumented with ASAN. There are some inputs causing attempting free on address which was not malloc. Here is the ASAN mode output:
==9252==ERROR: AddressSanitizer: attempting free on address which was not malloc()-ed: 0x60200000ef50 in thread T0
#0 ... | Bad-free with ASAN in mp42aac | https://api.github.com/repos/axiomatic-systems/Bento4/issues/765/comments | 0 | 2022-09-19T06:29:50Z | 2023-05-29T02:51:08Z | https://github.com/axiomatic-systems/Bento4/issues/765 | 1,377,466,423 | 765 |
CVE-2022-43034 | 2022-10-19T14:15:09.943 | An issue was discovered in Bento4 v1.6.0-639. There is a heap buffer overflow vulnerability in the AP4_BitReader::SkipBits(unsigned int) function in mp42ts. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/764"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/axiomatic-systems/Bento4/issues/764 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, developers of Bento4:
In the test of the binary mp42ts instrumented with ASAN. There are some inputs causing heap-buffer-overflow. Here is the ASAN mode output:
==10897==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x60300000ec3c at pc 0x0000004a9771 bp 0x7fffffffb150 sp 0x7fffffffb140
READ of size... | Heap-buffer-overflow with ASAN in mp42ts | https://api.github.com/repos/axiomatic-systems/Bento4/issues/764/comments | 0 | 2022-09-19T06:24:55Z | 2022-09-19T06:24:55Z | https://github.com/axiomatic-systems/Bento4/issues/764 | 1,377,462,592 | 764 |
CVE-2022-43035 | 2022-10-19T14:15:09.990 | An issue was discovered in Bento4 v1.6.0-639. There is a heap-buffer-overflow in AP4_Dec3Atom::AP4_Dec3Atom at Ap4Dec3Atom.cpp, leading to a Denial of Service (DoS), as demonstrated by mp42aac. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/762"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/axiomatic-systems/Bento4/issues/762 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, developers of Bento4:
Thanks for your fix of issue #751
In the test of the binary mp42aac instrumented with ASAN. There are some inputs causing heap-buffer-overflow. Here is the ASAN mode output:
==27304==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x60300000ed28 at pc 0x0000005a64d9 bp 0x7ffffff... | Heap-buffer-overflow with ASAN in mp42aac | https://api.github.com/repos/axiomatic-systems/Bento4/issues/762/comments | 0 | 2022-09-19T06:13:40Z | 2022-09-19T06:18:56Z | https://github.com/axiomatic-systems/Bento4/issues/762 | 1,377,452,573 | 762 |
CVE-2022-43037 | 2022-10-19T14:15:10.043 | An issue was discovered in Bento4 1.6.0-639. There is a memory leak in the function AP4_File::ParseStream in /Core/Ap4File.cpp. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/788"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"401"
] | 401 | https://github.com/axiomatic-systems/Bento4/issues/788 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, developers of Bento4:
In the test of the binary mp42aac instrumented with ASAN. There are some inputs causing memory leaks. Here is the ASAN mode output. The output is different from #763.
=================================================================
==6659==ERROR: LeakSanitizer: detected memory leaks
D... | Memory leaks with ASAN in mp42aac | https://api.github.com/repos/axiomatic-systems/Bento4/issues/788/comments | 0 | 2022-10-04T06:40:25Z | 2023-05-29T02:51:19Z | https://github.com/axiomatic-systems/Bento4/issues/788 | 1,395,742,603 | 788 |
CVE-2022-43038 | 2022-10-19T14:15:10.090 | Bento4 v1.6.0-639 was discovered to contain a heap overflow via the AP4_BitReader::ReadCache() function in mp42ts. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/787"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/axiomatic-systems/Bento4/issues/787 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, developers of Bento4:
In the test of the binary mp42ts instrumented with ASAN. There are some inputs causing heap-buffer-overflow. Here is the ASAN mode output. The output is different from #764
=================================================================
==3902==ERROR: AddressSanitizer: heap-buffer-overf... | Heap-buffer-overflow with ASAN in mp42ts | https://api.github.com/repos/axiomatic-systems/Bento4/issues/787/comments | 0 | 2022-10-04T06:36:03Z | 2023-05-29T02:51:18Z | https://github.com/axiomatic-systems/Bento4/issues/787 | 1,395,738,652 | 787 |
CVE-2022-43040 | 2022-10-19T14:15:10.183 | GPAC 2.1-DEV-rev368-gfd054169b-master was discovered to contain a heap buffer overflow via the function gf_isom_box_dump_start_ex at /isomedia/box_funcs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2280"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2280 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ### Description
Heap-buffer-overflow in isomedia/box_funcs.c:2074 in gf_isom_box_dump_start_ex
### Version
```
$ ./MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev368-gfd054169b-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your research:
GPA... | heap-buffer-overflow isomedia/box_funcs.c:2074 in gf_isom_box_dump_start_ex | https://api.github.com/repos/gpac/gpac/issues/2280/comments | 0 | 2022-10-09T08:31:37Z | 2022-10-10T15:44:28Z | https://github.com/gpac/gpac/issues/2280 | 1,402,198,804 | 2,280 |
CVE-2022-43042 | 2022-10-19T14:15:10.227 | GPAC 2.1-DEV-rev368-gfd054169b-master was discovered to contain a heap buffer overflow via the function FixSDTPInTRAF at isomedia/isom_intern.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2278"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2278 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ### Description
Heap-buffer-overflow in isomedia/isom_intern.c:227 in FixSDTPInTRAF
### Version
```
$ ./MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev368-gfd054169b-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your research:
GPAC Filters: ... | heap-buffer-overflow isomedia/isom_intern.c:227 in FixSDTPInTRAF | https://api.github.com/repos/gpac/gpac/issues/2278/comments | 0 | 2022-10-09T08:21:31Z | 2022-10-10T15:44:27Z | https://github.com/gpac/gpac/issues/2278 | 1,402,196,162 | 2,278 |
CVE-2022-40885 | 2022-10-19T18:15:13.287 | Bento4 v1.6.0-639 has a memory allocation issue that can cause denial of service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/761"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/yangfar/CVE/blob/main/CVE-2022-40885.md"
}... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"770"
] | 770 | https://github.com/axiomatic-systems/Bento4/issues/761 | [
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hello,I use the fuzzer(AFL) to fuzz binary mp42avc and got some crashes which show that allocator is out of memory trying to allocate 0xXXXXXXXX bytes when method new is called.
The following is the details.
### Bug1
#### ./mp42avc ~/out/crashes/id\:000017\,sig\:06\,src\:000925+000617\,op\:splice\,rep\:128 3.avc
==... | Out of memory in Ap4DataBuffer:new AP4_Byte[buffer_size] | https://api.github.com/repos/axiomatic-systems/Bento4/issues/761/comments | 0 | 2022-09-19T00:56:17Z | 2023-05-29T02:53:19Z | https://github.com/axiomatic-systems/Bento4/issues/761 | 1,377,242,122 | 761 |
CVE-2022-38870 | 2022-10-25T17:15:55.773 | Free5gc v3.2.1 is vulnerable to Information disclosure. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/free5gc/free5gc/issues/387"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:free5gc:free5gc:3.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "7EE8C66F-32FE-45C1-BC90-298A6B1469C7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"306"
] | 306 | https://github.com/free5gc/free5gc/issues/387 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"free5gc",
"free5gc"
] | ## Bug Description
Free5gc webconsole come with a default username Admin and by using this username as a token header and without any password or authentication ,it's possible to leak all the information below :
- Registered UEs (plmnID,ueId)
- Subscriber information (AccessType,CmState,Guti,Mcc,Mnc,Dnn,PduSessi... | [Bugs] Leaking Registered UEs,Subscriber information,Tenants and User via the Free5gc webconsole without authentication | https://api.github.com/repos/free5gc/free5gc/issues/387/comments | 4 | 2022-08-24T10:47:13Z | 2023-07-20T02:13:31Z | https://github.com/free5gc/free5gc/issues/387 | 1,349,239,716 | 387 |
CVE-2022-3662 | 2022-10-26T19:15:17.857 | A vulnerability was found in Axiomatic Bento4. It has been declared as critical. This vulnerability affects the function GetOffset of the file Ap4Sample.h of the component mp42hls. The manipulation leads to use after free. The attack can be initiated remotely. The exploit has been disclosed to the public and may be use... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 7.3,
"baseSeverity": "HIGH",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/files/9817606/mp42hls_cuaf_Ap4Sample99.zip"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"416"
] | 416 | https://github.com/axiomatic-systems/Bento4/issues/802 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, there.
There is an heap overflow in mp42hls, GetOffset, Ap4Sample.h:99, in the newest commit 5e7bb34a08272c49242196eba1cefab8af55f381. This seems to be an incomplete fix of issue #461.
Here is the reproducing command:
~~~~
./mp42hls poc
~~~~
POC:
[mp42hls_cuaf_Ap4Sample99.zip](https://github.com/axi... | Concurrent heap use after free in mp42hls, GetOffset, Ap4Sample.h:99 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/802/comments | 0 | 2022-10-19T06:53:27Z | 2023-05-29T02:40:07Z | https://github.com/axiomatic-systems/Bento4/issues/802 | 1,414,407,802 | 802 |
CVE-2022-3663 | 2022-10-26T19:15:19.093 | A vulnerability was found in Axiomatic Bento4. It has been rated as problematic. This issue affects the function AP4_StsdAtom of the file Ap4StsdAtom.cpp of the component MP4fragment. The manipulation leads to null pointer dereference. The attack may be initiated remotely. The exploit has been disclosed to the public a... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integ... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/files/9817303/mp4fragment_npd_Ap4StsdAtom.cpp75.zip"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/axiomatic-systems/Bento4/issues/800 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, there.
There is a segmentation fault caused by null pointer dereference in MP4fragment, Ap4StsdAtom.cpp:75 in the newest commit 5e7bb34a08272c49242196eba1cefab8af55f381.
The reason for this issue is that the return value of the GetSampleDescription is unchecked.
<img width="1055" alt="image" src="https://use... | Segmentation fault caused by null pointer dereference in MP4fragment, Ap4StsdAtom.cpp:75 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/800/comments | 0 | 2022-10-19T06:06:34Z | 2023-05-29T02:51:53Z | https://github.com/axiomatic-systems/Bento4/issues/800 | 1,414,350,784 | 800 |
CVE-2022-3664 | 2022-10-26T19:15:21.197 | A vulnerability classified as critical has been found in Axiomatic Bento4. Affected is the function AP4_BitStream::WriteBytes of the file Ap4BitStream.cpp of the component avcinfo. The manipulation leads to heap-based buffer overflow. It is possible to launch the attack remotely. The exploit has been disclosed to the p... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 7.3,
"baseSeverity": "HIGH",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/files/9746288/avcinfo_poc1.zip"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/axiomatic-systems/Bento4/issues/794 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hello, developers of Bento4!
I also found some **heap buffer overflow** bugs in avcinfo by using our fuzzing tools with ASAN.
Here is details:
## Bug1
```
=================================================================
==48171==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x602000000038 at pc 0x7f... | Some heap buffer overflow bugs exist in avcinfo | https://api.github.com/repos/axiomatic-systems/Bento4/issues/794/comments | 0 | 2022-10-10T13:34:03Z | 2023-05-29T02:51:50Z | https://github.com/axiomatic-systems/Bento4/issues/794 | 1,403,189,077 | 794 |
CVE-2022-3666 | 2022-10-26T19:15:23.570 | A vulnerability, which was classified as critical, has been found in Axiomatic Bento4. Affected by this issue is the function AP4_LinearReader::Advance of the file Ap4LinearReader.cpp of the component mp42ts. The manipulation leads to use after free. The attack may be launched remotely. The exploit has been disclosed t... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 7.3,
"baseSeverity": "HIGH",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/files/9744391/mp42ts_poc.zip"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"416"
] | 416 | https://github.com/axiomatic-systems/Bento4/issues/793 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hello, developers of Bento4. I found a heap use after free bug in AP4_LinearReader::Advance(bool) with ASAN.
The following is the details.
### Details
```
=================================================================
==32056==ERROR: AddressSanitizer: heap-use-after-free on address 0x604000001f98 at pc 0x5609... | heap-use-after-free bug in mp42ts | https://api.github.com/repos/axiomatic-systems/Bento4/issues/793/comments | 0 | 2022-10-10T08:51:58Z | 2023-05-29T02:51:21Z | https://github.com/axiomatic-systems/Bento4/issues/793 | 1,402,818,781 | 793 |
CVE-2022-3667 | 2022-10-26T19:15:24.427 | A vulnerability, which was classified as critical, was found in Axiomatic Bento4. This affects the function AP4_MemoryByteStream::WritePartial of the file Ap4ByteStream.cpp of the component mp42aac. The manipulation leads to heap-based buffer overflow. It is possible to initiate the attack remotely. The exploit has bee... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 7.3,
"baseSeverity": "HIGH",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/17ssDP/fuzzer_crashes/blob/main/Bento4/mp42aac-hbo-01"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/axiomatic-systems/Bento4/issues/789 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, developers of Bento4:
Thanks for your fix of issue #751
In the test of the binary mp42aac instrumented with ASAN. There are some inputs causing heap-buffer-overflow. Here is the ASAN mode output. This issue may be because of an incomplete fix of #751.
===========================================================... | Heap-buffer-overflow with ASAN in mp42aac | https://api.github.com/repos/axiomatic-systems/Bento4/issues/789/comments | 0 | 2022-10-04T06:45:46Z | 2023-05-29T02:51:19Z | https://github.com/axiomatic-systems/Bento4/issues/789 | 1,395,747,445 | 789 |
CVE-2022-3668 | 2022-10-26T19:15:25.300 | A vulnerability has been found in Axiomatic Bento4 and classified as problematic. This vulnerability affects the function AP4_AtomFactory::CreateAtomFromStream of the component mp4edit. The manipulation leads to memory leak. The attack can be initiated remotely. The exploit has been disclosed to the public and may be u... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integ... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/files/9640968/Bug_1_POC.zip"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"401"
] | 401 | https://github.com/axiomatic-systems/Bento4/issues/776 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # Summary
Hi, developers of Bento4:
I tested the binary mp4edit and mp42hevc with my fuzzer, and three crashes incurred, including two memory-leaks from mp4edit and a heap-overflow from mp42hevc. And I think Bug1 and Bug2 are different. The following is the details.
# Bug1
Detected memory leaks in mp4edit.
```... | Memory-leak and heap-overflow bugs in Bento4 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/776/comments | 0 | 2022-09-25T14:31:41Z | 2023-05-29T02:51:14Z | https://github.com/axiomatic-systems/Bento4/issues/776 | 1,385,048,849 | 776 |
CVE-2022-43280 | 2022-10-28T21:15:09.807 | wasm-interp v1.0.29 was discovered to contain an out-of-bounds read via the component OnReturnCallExpr->GetReturnCallDropKeepCount. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/WebAssembly/wabt/issues/1982"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:wabt:1.0.29:*:*:*:*:*:*:*",
"matchCriteriaId": "C524E018-FAA2-4A8D-B861-6ACE6A675FEC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"125"
] | 125 | https://github.com/WebAssembly/wabt/issues/1982 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"WebAssembly",
"wabt"
] | ### Environment
```
OS : Linux ubuntu 5.15.0-46-generic #49~20.04.1-Ubuntu SMP Thu Aug 4 19:15:44 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
Commit : 3054d61f703d609995798f872fc86b462617c294
Version : 1.0.29
Build : make clang-debug-asan
```
### Proof of concept
poc-interp-2.wasm
[poc-interp-2.wasm.zip]... | Out-of-bound read in OnReturnCallExpr->GetReturnCallDropKeepCount | https://api.github.com/repos/WebAssembly/wabt/issues/1982/comments | 1 | 2022-09-05T12:50:49Z | 2022-09-17T19:13:47Z | https://github.com/WebAssembly/wabt/issues/1982 | 1,361,906,900 | 1,982 |
CVE-2022-43281 | 2022-10-28T21:15:09.883 | wasm-interp v1.0.29 was discovered to contain a heap overflow via the component std::vector<wabt::Type, std::allocator<wabt::Type>>::size() at /bits/stl_vector.h. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/WebAssembly/wabt/issues/1981"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:wasm:1.0.29:*:*:*:*:*:*:*",
"matchCriteriaId": "FC0B0732-FA64-456C-9C9E-FC4F182BEEB1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/WebAssembly/wabt/issues/1981 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"WebAssembly",
"wabt"
] | ### Environment
```
OS : Linux ubuntu 5.15.0-46-generic #49~20.04.1-Ubuntu SMP Thu Aug 4 19:15:44 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
Commit : 3054d61f703d609995798f872fc86b462617c294
Version : 1.0.29
Build : make clang-debug-asan
```
### Proof of concept
poc-interp-1.wasm
[poc-interp-1.wasm.... | heap overflow in wasm-interp | https://api.github.com/repos/WebAssembly/wabt/issues/1981/comments | 1 | 2022-09-05T12:50:09Z | 2022-09-17T19:11:15Z | https://github.com/WebAssembly/wabt/issues/1981 | 1,361,905,751 | 1,981 |
CVE-2022-43282 | 2022-10-28T21:15:09.940 | wasm-interp v1.0.29 was discovered to contain an out-of-bounds read via the component OnReturnCallIndirectExpr->GetReturnCallDropKeepCount. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/WebAssembly/wabt/issues/1983"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:wabt:1.0.29:*:*:*:*:*:*:*",
"matchCriteriaId": "C524E018-FAA2-4A8D-B861-6ACE6A675FEC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"125"
] | 125 | https://github.com/WebAssembly/wabt/issues/1983 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"WebAssembly",
"wabt"
] | ### Environment
```
OS : Linux ubuntu 5.15.0-46-generic #49~20.04.1-Ubuntu SMP Thu Aug 4 19:15:44 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
Commit : 3054d61f703d609995798f872fc86b462617c294
Version : 1.0.29
Build : make clang-debug-asan
```
### Proof of concept
poc-interp-3.wasm
[poc-interp-3.wasm.zip]... | Out-of-bound read in OnReturnCallIndirectExpr->GetReturnCallDropKeepCount | https://api.github.com/repos/WebAssembly/wabt/issues/1983/comments | 1 | 2022-09-05T12:51:24Z | 2022-09-17T19:15:54Z | https://github.com/WebAssembly/wabt/issues/1983 | 1,361,907,936 | 1,983 |
CVE-2022-43283 | 2022-10-28T21:15:10.007 | wasm2c v1.0.29 was discovered to contain an abort in CWriter::Write. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/WebAssembly/wabt/issues/1985"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:wabt:1.0.29:*:*:*:*:*:*:*",
"matchCriteriaId": "C524E018-FAA2-4A8D-B861-6ACE6A675FEC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"434"
] | 434 | https://github.com/WebAssembly/wabt/issues/1985 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"WebAssembly",
"wabt"
] | ### Environment
```
OS : Linux ubuntu 5.15.0-46-generic #49~20.04.1-Ubuntu SMP Thu Aug 4 19:15:44 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
Commit : 3054d61f703d609995798f872fc86b462617c294
Version : 1.0.29
Build : make clang-debug-asan
```
### Proof of concept
poc_wasm2c-1.wasm
[poc_wasm2c-1.wasm.zip]... | Aborted in CWriter::Write at wasm2c | https://api.github.com/repos/WebAssembly/wabt/issues/1985/comments | 1 | 2022-09-05T12:58:25Z | 2022-10-03T06:27:37Z | https://github.com/WebAssembly/wabt/issues/1985 | 1,361,920,430 | 1,985 |
CVE-2022-3784 | 2022-10-31T21:15:12.497 | A vulnerability classified as critical was found in Axiomatic Bento4 5e7bb34. Affected by this vulnerability is the function AP4_Mp4AudioDsiParser::ReadBits of the file Ap4Mp4AudioInfo.cpp of the component mp4hls. The manipulation leads to heap-based buffer overflow. The attack can be launched remotely. The exploit has... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 6.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integr... | [
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/files/9849116/mp42hls_ReadBits_Ap4Mp4AudioInfo66.zip"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/axiomatic-systems/Bento4/issues/806 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, there.
There is an heap overflow in ReadBits, Ap4Mp4AudioInfo.cpp:66, in the newest master branch 5e7bb34a08272c49242196eba1cefab8af55f381, which seems to be incomplete fix of issue #194.
Here is the reproducing command:
~~~~
mp42hls poc
~~~~
POC:
[mp42hls_ReadBits_Ap4Mp4AudioInfo66.zip](https://git... | Heap overflow in mp4hls, ReadBits, Ap4Mp4AudioInfo.cpp:66 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/806/comments | 0 | 2022-10-24T06:03:44Z | 2023-05-29T02:38:17Z | https://github.com/axiomatic-systems/Bento4/issues/806 | 1,420,268,717 | 806 |
CVE-2022-3785 | 2022-10-31T21:15:12.577 | A vulnerability, which was classified as critical, has been found in Axiomatic Bento4. Affected by this issue is the function AP4_DataBuffer::SetDataSize of the component Avcinfo. The manipulation leads to heap-based buffer overflow. The attack may be launched remotely. The exploit has been disclosed to the public and ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 6.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integr... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/files/9658653/POC_avcinfo_15644345.zip"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/axiomatic-systems/Bento4/issues/780 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # Summary
Hi, developers of Bento4:
I tested the binary Avcinfo with my fuzzer, and a crash incurred—heap-buffer-overflow. The following is the details. I think this error is different from both #731 and #610.
# Bug
Detected heap-buffer-overflow in Avcinfo.
```
root@4w41awdas71:/# ./Bento4/cmakebuild/avcinfo ... | A heap-buffer-overflow in Avcinfo | https://api.github.com/repos/axiomatic-systems/Bento4/issues/780/comments | 3 | 2022-09-27T18:09:33Z | 2023-05-29T02:51:16Z | https://github.com/axiomatic-systems/Bento4/issues/780 | 1,388,166,902 | 780 |
CVE-2022-3807 | 2022-11-01T20:15:22.120 | A vulnerability was found in Axiomatic Bento4. It has been rated as problematic. Affected by this issue is some unknown functionality of the component Incomplete Fix CVE-2019-13238. The manipulation leads to resource consumption. The attack may be launched remotely. The exploit has been disclosed to the public and may ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 4.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integ... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/files/9820612/mp42aac_exhaustive_AP4_RtpAtom50.zip"
},
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:-:*:*:*:*:*:*:*",
"matchCriteriaId": "C9F13899-4DE7-4BC0-8E7F-8795F58AA99F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"252"
] | 252 | https://github.com/axiomatic-systems/Bento4/issues/803 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | A memory allocation failure unhandled in Ap4RtpAtom.cpp and leads to crashes. This seems to be an incomplete fix of issue #396, CVE-2019-13238.
`./mp42aac input_file /dev/null`
In file Source/C++/Core/Ap4RtpAtom.cpp
<img width="929" alt="image" src="https://user-images.githubusercontent.com/7632714/196694985-02c... | Incomplete fix of CVE-2019-13238, Exhaustive memory misunhandle | https://api.github.com/repos/axiomatic-systems/Bento4/issues/803/comments | 0 | 2022-10-19T12:55:56Z | 2022-10-19T12:55:56Z | https://github.com/axiomatic-systems/Bento4/issues/803 | 1,414,926,196 | 803 |
CVE-2022-3812 | 2022-11-01T22:15:12.027 | A vulnerability was found in Axiomatic Bento4. It has been rated as problematic. Affected by this issue is the function AP4_ContainerAtom::AP4_ContainerAtom of the component mp4encrypt. The manipulation leads to memory leak. The attack may be launched remotely. The exploit has been disclosed to the public and may be us... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 4.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integ... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/files/9726934/POC_mp4encrypt_631000973.zip"
},
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"401"
] | 401 | https://github.com/axiomatic-systems/Bento4/issues/792 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # **Summary**
Hi, developers of Bento4,
I tested the binary of bento4 with my fuzzer, and some memory-leak crashes incurred. Among them, Bug3-5 may be different from #771. The operation system is Ubuntu 18.04.6 LTS (docker), these crashes with the following.
# **Bug1**
Detected memory leaks in mp4encrypt, the bug... | Some Memory leaks exist in mp4xx | https://api.github.com/repos/axiomatic-systems/Bento4/issues/792/comments | 0 | 2022-10-06T17:14:56Z | 2023-06-26T05:55:54Z | https://github.com/axiomatic-systems/Bento4/issues/792 | 1,400,040,986 | 792 |
CVE-2022-43254 | 2022-11-02T14:15:15.637 | GPAC v2.1-DEV-rev368-gfd054169b-master was discovered to contain a memory leak via the component gf_list_new at utils/list.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2284"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"401"
] | 401 | https://github.com/gpac/gpac/issues/2284 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ### Description
Memory Leak in gf_list_new utils/list.c:601
### Version
```
$ ./MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev368-gfd054169b-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your research:
GPAC Filters: https://doi.org/10.114... | Memory Leak in gf_list_new utils/list.c:601 | https://api.github.com/repos/gpac/gpac/issues/2284/comments | 0 | 2022-10-11T07:44:42Z | 2022-10-11T11:02:16Z | https://github.com/gpac/gpac/issues/2284 | 1,404,158,827 | 2,284 |
CVE-2022-43255 | 2022-11-02T14:15:15.917 | GPAC v2.1-DEV-rev368-gfd054169b-master was discovered to contain a memory leak via the component gf_odf_new_iod at odf/odf_code.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2285"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"401"
] | 401 | https://github.com/gpac/gpac/issues/2285 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ### Description
Memory Leak in gf_odf_new_iod odf/odf_code.c:415
### Version
```
$ ./MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev368-gfd054169b-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your research:
GPAC Filters: https://doi.org/1... | Memory Leak in gf_odf_new_iod odf/odf_code.c:415 | https://api.github.com/repos/gpac/gpac/issues/2285/comments | 0 | 2022-10-11T07:56:13Z | 2022-10-11T11:02:17Z | https://github.com/gpac/gpac/issues/2285 | 1,404,173,443 | 2,285 |
CVE-2022-43372 | 2022-11-03T18:15:17.987 | Emlog Pro v1.7.1 was discovered to contain a reflected cross-site scripting (XSS) vulnerability at /admin/store.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/emlog/emlog/issues/195"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:emlog:emlog:1.7.1:*:*:*:pro:*:*:*",
"matchCriteriaId": "BFC4BB7B-FCA0-4826-AD2E-790A7DBBDD17",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/emlog/emlog/issues/195 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"emlog",
"emlog"
] | ### **Which version of emlog do you using?**
emlog_pro_1.7.1
### **Expected behavior**
Search store templates
### **Actual behavior**
Reflected XSS vulnerabilities
### **Steps to reproduce the behavior**
> Url:https://github.com/emlog/emlog/blob/master/admin/store.php
>
> poc:"%2F><img+src%3Dx+onerror%3Dale... | Reflected-XSS vulnerabilities via '/admin/store.php' #1 | https://api.github.com/repos/emlog/emlog/issues/195/comments | 1 | 2022-10-16T17:27:37Z | 2022-10-19T15:57:30Z | https://github.com/emlog/emlog/issues/195 | 1,410,558,751 | 195 |
CVE-2022-45061 | 2022-11-09T07:15:09.887 | An issue was discovered in Python before 3.11.1. An unnecessary quadratic algorithm exists in one path when processing some inputs to the IDNA (RFC 3490) decoder, such that a crafted, unreasonably long name being presented to the decoder could lead to a CPU denial of service. Hostnames are often supplied by remote serv... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/python/cpython/issues/98433"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.debian.org/debian-lts-announce/2023/05/msg00024.html"
}... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:python:python:*:*:*:*:*:*:*:*",
"matchCriteriaId": "20A23D09-CFA7-4028-A5E9-7AD784C2B9D8",
"versionEndExcluding": null,
"versionEndIncluding": "3.7.15",
"versionStartExcludin... | [
"407"
] | 407 | https://github.com/python/cpython/issues/98433 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"python",
"cpython"
] | # Bug report
Originally reported to the security address on September 9.
```python
('xn--016c'+'a'*5000).encode('utf-8').decode('idna')
```
The execution time is not linear in relation to the input string size, which can cause slowness with large inputs:
10 chars = 0.016 seconds
100 chars = 0.047 seconds... | Slow IDNA decoding with large strings [CVE-2022-45061] | https://api.github.com/repos/python/cpython/issues/98433/comments | 4 | 2022-10-19T06:12:24Z | 2022-11-09T10:50:40Z | https://github.com/python/cpython/issues/98433 | 1,414,357,245 | 98,433 |
CVE-2022-3974 | 2022-11-13T10:15:10.333 | A vulnerability classified as critical was found in Axiomatic Bento4. Affected by this vulnerability is the function AP4_StdcFileByteStream::ReadPartial of the file Ap4StdCFileByteStream.cpp of the component mp4info. The manipulation leads to heap-based buffer overflow. The attack can be launched remotely. The exploit ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 6.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integr... | [
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/files/9987970/mp4info_overflow_ReadPartial341.zip"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:2022-10-08:*:*:*:*:*:*:*",
"matchCriteriaId": "E6D96205-9447-4E3E-B05C-A45E8353CF6C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"787"
] | 787 | https://github.com/axiomatic-systems/Bento4/issues/812 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, there.
There is an heap overflow in ReadPartial, Ap4StdCFileByteStream.cpp:341, in the newest master branch 5e7bb34a08272c49242196eba1cefab8af55f381, which seems to be incomplete fix of issue #510.
Here is the reproducing command:
~~~~
mp42info poc
~~~~
POC:
[mp4info_overflow_ReadPartial341.zip](htt... | Heap overflow in mp4info, ReadPartial, Ap4StdCFileByteStream.cpp:341 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/812/comments | 0 | 2022-11-11T07:45:28Z | 2022-11-11T07:46:10Z | https://github.com/axiomatic-systems/Bento4/issues/812 | 1,445,073,819 | 812 |
CVE-2022-43323 | 2022-11-14T20:15:17.740 | EyouCMS V1.5.9-UTF8-SP1 was discovered to contain a Cross-Site Request Forgery (CSRF) via the Top Up Balance component under the Edit Member module. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/28#issue-1410026516"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracki... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.5.9:*:*:*:*:*:*:*",
"matchCriteriaId": "42A15197-E862-429C-8ECB-79D0B850C9C5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"352"
] | 352 | https://github.com/weng-xianhu/eyoucms/issues/28#issue-1410026516 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | EyouCMS v1.5.9 has a vulnerability, Cross-site request forgery(CSRF).Located in the backend, member center, editing, Top up balance. To exploit this vulnerability, a quasi-prepared HTML file needs to be opened
1、Go to the background --> member center--> edit member--> Top up balance
 | https://api.github.com/repos/weng-xianhu/eyoucms/issues/28/comments | 1 | 2022-10-15T03:24:29Z | 2023-02-28T02:38:05Z | https://github.com/weng-xianhu/eyoucms/issues/28 | 1,410,026,516 | 28 |
CVE-2022-44387 | 2022-11-14T20:15:18.233 | EyouCMS V1.5.9-UTF8-SP1 was discovered to contain a Cross-Site Request Forgery (CSRF) via the Basic Information component under the Edit Member module. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/29"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.5.9:*:*:*:*:*:*:*",
"matchCriteriaId": "42A15197-E862-429C-8ECB-79D0B850C9C5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"352"
] | 352 | https://github.com/weng-xianhu/eyoucms/issues/29 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | EyouCMS v1.5.9 has a vulnerability, Cross-site request forgery(CSRF).Located in the backend, member center, edit member profile. To exploit this vulnerability, a constructed HTML file needs to be opened
1. Enter the background - > member center - > edit members - > basic information
 | https://api.github.com/repos/weng-xianhu/eyoucms/issues/29/comments | 1 | 2022-10-27T13:36:23Z | 2023-02-24T07:42:24Z | https://github.com/weng-xianhu/eyoucms/issues/29 | 1,425,651,916 | 29 |
CVE-2022-44389 | 2022-11-14T20:15:18.593 | EyouCMS V1.5.9-UTF8-SP1 was discovered to contain a Cross-Site Request Forgery (CSRF) via the Edit Admin Profile module. This vulnerability allows attackers to arbitrarily change Administrator account information. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/30"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.5.9:*:*:*:*:*:*:*",
"matchCriteriaId": "42A15197-E862-429C-8ECB-79D0B850C9C5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"352"
] | 352 | https://github.com/weng-xianhu/eyoucms/issues/30 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | EyouCMS v1.5.9 has a vulnerability, Cross-site request forgery(CSRF).Located in the background, edit the administrator profile. This vulnerability may cause the modification of personal information such as administrator password, mobile phone number, and email address. To exploit this vulnerability, a constructed HTML ... | EyouCMS v1.5.9 has a vulnerability, Cross-site request forgery(CSRF) | https://api.github.com/repos/weng-xianhu/eyoucms/issues/30/comments | 1 | 2022-10-29T03:58:24Z | 2023-02-21T02:49:11Z | https://github.com/weng-xianhu/eyoucms/issues/30 | 1,428,062,999 | 30 |
CVE-2022-44390 | 2022-11-14T20:15:18.950 | A cross-site scripting (XSS) vulnerability in EyouCMS V1.5.9-UTF8-SP1 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Public Security Record Number text field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/31"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.5.9:*:*:*:*:*:*:*",
"matchCriteriaId": "42A15197-E862-429C-8ECB-79D0B850C9C5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/weng-xianhu/eyoucms/issues/31 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | Version:V1.5.9-UTF8-SP1

1、Go to the background --> basic information--> the record number and public security record number, and click the code mode to modify to the code mode.
 | https://api.github.com/repos/weng-xianhu/eyoucms/issues/31/comments | 1 | 2022-10-29T06:04:09Z | 2023-02-21T01:49:51Z | https://github.com/weng-xianhu/eyoucms/issues/31 | 1,428,108,510 | 31 |
CVE-2022-43183 | 2022-11-17T21:15:15.837 | XXL-Job before v2.3.1 contains a Server-Side Request Forgery (SSRF) via the component /admin/controller/JobLogController.java. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/xuxueli/xxl-job/issues/3002"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xuxueli:xxl-job:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B9117C48-ADBB-4018-8476-F291CA8A2BF4",
"versionEndExcluding": null,
"versionEndIncluding": "2.3.1",
"versionStartExcludi... | [
"918"
] | 918 | https://github.com/xuxueli/xxl-job/issues/3002 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"xuxueli",
"xxl-job"
] | xxl-job =< 2.3.1 version (latest version) has SSRF vulnerability, which causes low-privileged users to control executor to execute arbitrary commands
1. Vulnerability description
XXL-JOB is a distributed task scheduling platform based on java language in the XXL (XXL-JOB) community.
There is an SSRF vulnerabi... | xxl-job =< 2.3.1 version (latest version) has SSRF vulnerability, which causes low-privileged users to control executor to execute arbitrary commands | https://api.github.com/repos/xuxueli/xxl-job/issues/3002/comments | 5 | 2022-10-10T06:59:34Z | 2023-03-23T10:51:45Z | https://github.com/xuxueli/xxl-job/issues/3002 | 1,402,687,023 | 3,002 |
CVE-2022-38871 | 2022-11-18T23:15:20.117 | In Free5gc v3.0.5, the AMF breaks due to malformed NAS messages. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/free5gc/free5gc/issues/198"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:free5gc:free5gc:3.0.5:*:*:*:*:*:*:*",
"matchCriteriaId": "7AC5244A-13E0-4776-A4C6-58A9784FDAFF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"400"
] | 400 | https://github.com/free5gc/free5gc/issues/198 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"free5gc",
"free5gc"
] | ## Describe the bug
While testing the free5gc AMF for some NAS basic security features and fuzzing, I could trigger several crashes, while sending malformed NAS message. This means those issues are relatively exposed as they can be trigger by any 5G subscriber, in the principle.
Here, all memory issues due to mishand... | [Bugs] AMF breaks due to malformed NAS message | https://api.github.com/repos/free5gc/free5gc/issues/198/comments | 4 | 2021-04-26T13:42:33Z | 2023-12-04T08:48:27Z | https://github.com/free5gc/free5gc/issues/198 | 867,719,689 | 198 |
CVE-2022-45280 | 2022-11-23T21:15:11.310 | A cross-site scripting (XSS) vulnerability in the Url parameter in /login.php of EyouCMS v1.6.0 allows attackers to execute arbitrary web scripts or HTML via a crafted payload. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/32"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.0:*:*:*:*:*:*:*",
"matchCriteriaId": "EB987CAE-6D4D-417A-8E0D-9DCC47F986EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/weng-xianhu/eyoucms/issues/32 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | name:EyouCMS
version: EyouCMS-V1.6.0-UTF8-SP1
Installation package [download:](https://www.eyoucms.com/rizhi/2022/1102/28642.html)
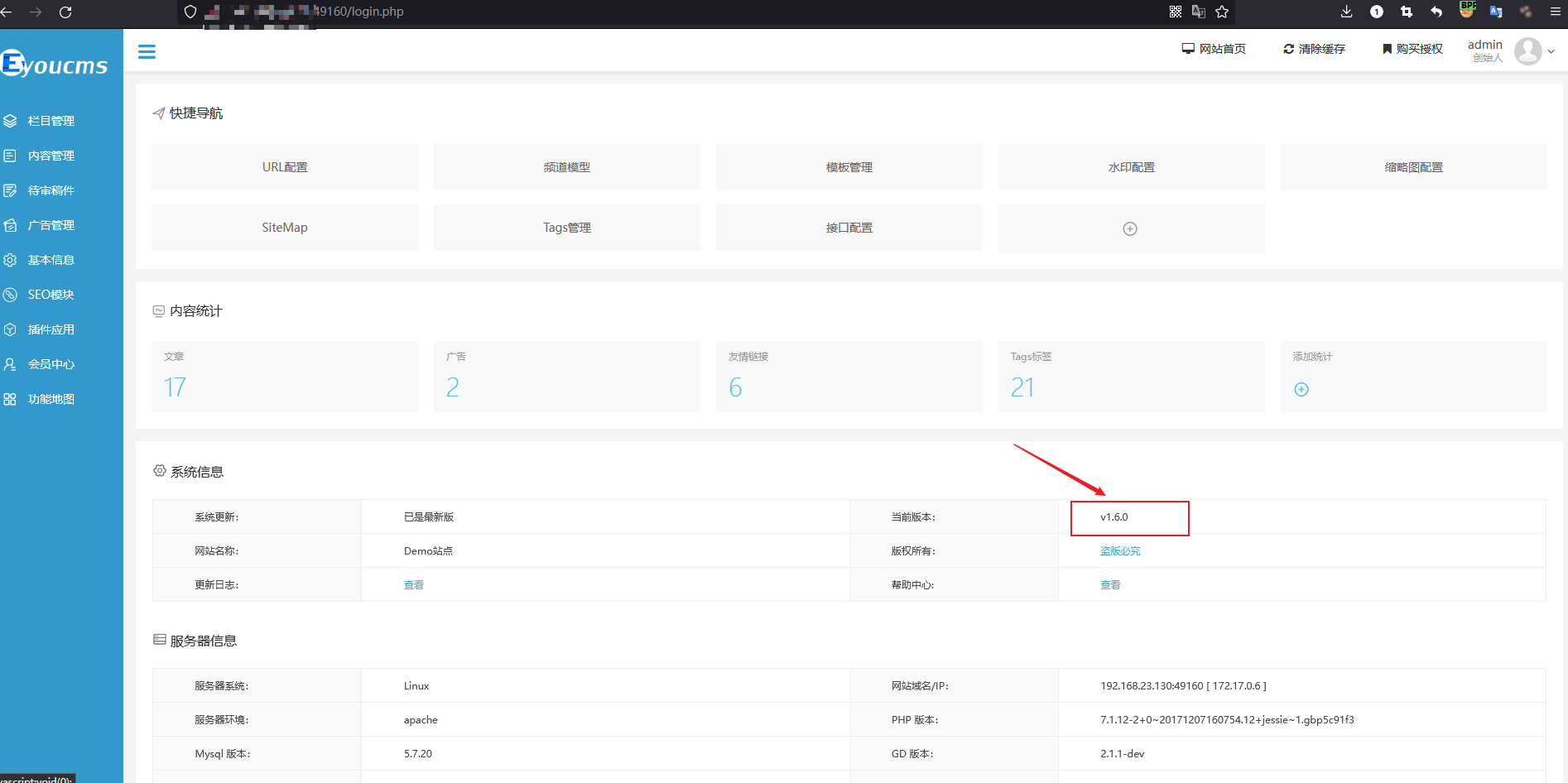
Problematic packets:
> POST /login.php?m=admin&c=Links&a=add&_ajax=1... | EyouCMS v1.6.0 existence stored cross-site scripting (XSS) | https://api.github.com/repos/weng-xianhu/eyoucms/issues/32/comments | 1 | 2022-11-10T12:16:56Z | 2023-02-21T01:34:50Z | https://github.com/weng-xianhu/eyoucms/issues/32 | 1,443,805,273 | 32 |
CVE-2022-45205 | 2022-11-25T17:15:11.007 | Jeecg-boot v3.4.3 was discovered to contain a SQL injection vulnerability via the component /sys/dict/queryTableData. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://jeecg-boot.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jeecgboot/jeecg-boot/issues/4128"
},
{
"s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecg:jeecg_boot:3.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "49DF84AE-6D1A-4065-AB0B-CB6926D6C5F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"89"
] | 89 | https://github.com/jeecgboot/jeecg-boot/issues/4128 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jeecgboot",
"jeecg-boot"
] | # SysDictMapper.xml
queryDictTablePageList。You can see that no precompiling is performed
<img width="960" alt="截屏2022-10-25 15 24 58" src="https://user-images.githubusercontent.com/60163868/197709842-99880e4f-25e4-4f5a-a2cb-4fa8dcca4db2.png">
# SysDictController.java
<img width="1192" alt="截屏2022-10-25 15 25 29" ... | [CVE-2022-45205]/sys/dict/queryTableData is affected by sql injection | https://api.github.com/repos/jeecgboot/JeecgBoot/issues/4128/comments | 2 | 2022-10-25T07:31:16Z | 2022-12-01T07:35:33Z | https://github.com/jeecgboot/JeecgBoot/issues/4128 | 1,421,998,736 | 4,128 |
CVE-2022-45206 | 2022-11-25T17:15:11.060 | Jeecg-boot v3.4.3 was discovered to contain a SQL injection vulnerability via the component /sys/duplicate/check. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://jeecg-boot.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jeecgboot/jeecg-boot/issues/4129"
},
{
"s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecg:jeecg_boot:3.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "49DF84AE-6D1A-4065-AB0B-CB6926D6C5F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"89"
] | 89 | https://github.com/jeecgboot/jeecg-boot/issues/4129 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jeecgboot",
"jeecg-boot"
] | [jeecg-boot漏洞.pdf](https://github.com/jeecgboot/jeecg-boot/files/9858362/jeecg-boot.pdf)
| [CVE-2022-45206]/sys/duplicate/check存在sql注入漏洞 | https://api.github.com/repos/jeecgboot/JeecgBoot/issues/4129/comments | 12 | 2022-10-25T08:10:59Z | 2024-04-21T07:44:09Z | https://github.com/jeecgboot/JeecgBoot/issues/4129 | 1,422,048,340 | 4,129 |
CVE-2022-45207 | 2022-11-25T17:15:11.117 | Jeecg-boot v3.4.3 was discovered to contain a SQL injection vulnerability via the component updateNullByEmptyString. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://jeecg-boot.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jeecgboot/jeecg-boot/issues/4127"
},
{
"s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecg:jeecg_boot:3.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "49DF84AE-6D1A-4065-AB0B-CB6926D6C5F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"89"
] | 89 | https://github.com/jeecgboot/jeecg-boot/issues/4127 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jeecgboot",
"jeecg-boot"
] | java提供了原生的预编译sql语句,这样可以防止sql注入问题
# queryListWithPermission
下图没有进行预编译处理,建议换成#{},虽然项目现在没有使用这条语句,但不排除以后的可能,建议修复
<img width="1532" alt="截屏2022-10-25 10 48 22" src="https://user-images.githubusercontent.com/60163868/197670494-95f85eb2-ce58-43ee-9aef-02b9e07ba2b1.png">
# updateNullByEmptyString
下图也使用的是${}
<img width="1... | [CVE-2022-45207]这里有几处没有换成预编译,但个人建议修复 | https://api.github.com/repos/jeecgboot/JeecgBoot/issues/4127/comments | 6 | 2022-10-25T06:07:32Z | 2022-12-07T00:59:38Z | https://github.com/jeecgboot/JeecgBoot/issues/4127 | 1,421,911,807 | 4,127 |
CVE-2022-45208 | 2022-11-25T17:15:11.173 | Jeecg-boot v3.4.3 was discovered to contain a SQL injection vulnerability via the component /sys/user/putRecycleBin. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://jeecg-boot.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jeecgboot/jeecg-boot/issues/4126"
},
{
"s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecg:jeecg_boot:3.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "49DF84AE-6D1A-4065-AB0B-CB6926D6C5F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"89"
] | 89 | https://github.com/jeecgboot/jeecg-boot/issues/4126 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jeecgboot",
"jeecg-boot"
] | # sysUserMapper.xml
revertLogicDeleted. You can see that no precompiling is performed
<img width="1048" alt="截屏2022-10-25 11 40 04" src="https://user-images.githubusercontent.com/60163868/197676949-8016d0d1-9874-45fd-ba3f-89c63d8a2c90.png">
# SysUserController.java
<img width="1278" alt="截屏2022-10-25 11 40 32" sr... | [CVE-2022-45208]/sys/user/putRecycleBin is affected by sql injection | https://api.github.com/repos/jeecgboot/JeecgBoot/issues/4126/comments | 2 | 2022-10-25T03:44:24Z | 2022-12-07T01:05:07Z | https://github.com/jeecgboot/JeecgBoot/issues/4126 | 1,421,795,524 | 4,126 |
CVE-2022-45210 | 2022-11-25T17:15:11.230 | Jeecg-boot v3.4.3 was discovered to contain a SQL injection vulnerability via the component /sys/user/deleteRecycleBin. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://jeecg-boot.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jeecgboot/jeecg-boot/issues/4125"
},
{
"s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecg:jeecg_boot:3.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "49DF84AE-6D1A-4065-AB0B-CB6926D6C5F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"89"
] | 89 | https://github.com/jeecgboot/jeecg-boot/issues/4125 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jeecgboot",
"jeecg-boot"
] | # sysUserMapper.xml
deleteLogicDeleted. You can see that no precompiling is performed
<img width="617" alt="截屏2022-10-25 11 04 50" src="https://user-images.githubusercontent.com/60163868/197672626-fb8257e3-ca86-484e-a4aa-e878ebb31c34.png">
# SysUserController.java
<img width="811" alt="截屏2022-10-25 11 06 04" src="... | [CVE-2022-45210]/sys/user/deleteRecycleBin is affected by sql injection | https://api.github.com/repos/jeecgboot/JeecgBoot/issues/4125/comments | 2 | 2022-10-25T03:12:40Z | 2022-12-07T01:16:36Z | https://github.com/jeecgboot/JeecgBoot/issues/4125 | 1,421,774,671 | 4,125 |
CVE-2022-45202 | 2022-11-29T04:15:11.207 | GPAC v2.1-DEV-rev428-gcb8ae46c8-master was discovered to contain a stack overflow via the function dimC_box_read at isomedia/box_code_3gpp.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2296"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2296 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ### Description
Stack buffer overflow in function dimC_box_read at isomedia/box_code_3gpp.c:1070
### System info
ubuntu 20.04 lts
### version info:
···
/MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev428-gcb8ae46c8-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please ... | Stack buffer overflow in function dimC_box_read at isomedia/box_code_3gpp.c:1070 | https://api.github.com/repos/gpac/gpac/issues/2296/comments | 1 | 2022-10-31T01:21:46Z | 2022-11-04T08:28:44Z | https://github.com/gpac/gpac/issues/2296 | 1,429,110,423 | 2,296 |
CVE-2022-45204 | 2022-11-29T04:15:11.253 | GPAC v2.1-DEV-rev428-gcb8ae46c8-master was discovered to contain a memory leak via the function dimC_box_read at isomedia/box_code_3gpp.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2307"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"401"
] | 401 | https://github.com/gpac/gpac/issues/2307 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ### Description
Memory Leak in dimC_box_read at isomedia/box_code_3gpp.c:1060
### System info
ubuntu 20.04 lts
###
version info:
```
./MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev460-g9d963dc62-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in y... | Memory Leak in dimC_box_read at isomedia/box_code_3gpp.c:1060 | https://api.github.com/repos/gpac/gpac/issues/2307/comments | 1 | 2022-11-07T12:35:15Z | 2022-11-08T02:28:56Z | https://github.com/gpac/gpac/issues/2307 | 1,438,293,014 | 2,307 |
CVE-2022-45343 | 2022-11-29T16:15:09.293 | GPAC v2.1-DEV-rev478-g696e6f868-master was discovered to contain a heap use-after-free via the Q_IsTypeOn function at /gpac/src/bifs/unquantize.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2315"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"416"
] | 416 | https://github.com/gpac/gpac/issues/2315 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | # Description
Heap use after free in Q_IsTypeOn at gpac/src/bifs/unquantize.c:175:12
# System info
Ubuntu 20.04 lts
# Version info
```shell
MP4Box - GPAC version 2.1-DEV-rev478-g696e6f868-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your r... | Heap use after free in Q_IsTypeOn at gpac/src/bifs/unquantize.c | https://api.github.com/repos/gpac/gpac/issues/2315/comments | 0 | 2022-11-14T01:55:34Z | 2022-11-14T13:45:21Z | https://github.com/gpac/gpac/issues/2315 | 1,447,239,893 | 2,315 |
CVE-2022-45332 | 2022-11-30T03:15:13.973 | LibreDWG v0.12.4.4643 was discovered to contain a heap buffer overflow via the function decode_preR13_section_hdr at decode_r11.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/524"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.12.4.4643:*:*:*:*:*:*:*",
"matchCriteriaId": "8B1D693A-7DFD-40CC-B3E7-D2B6E5F5ADD1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/LibreDWG/libredwg/issues/524 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | **System info**
Ubuntu x86_64, clang 10.0
version: 0.12.4.4643, last commit [93c2512](https://github.com/LibreDWG/libredwg/commit/93c25124c191987af168ace9fe4b5623061874bd)
**Command line**
./dwg2dxf poc
**Poc**
poc: [poc](https://github.com/iorra-cifer/Poc/blob/main/libredwg/heap-buffer-overflow?raw=true)
... | heap-buffer-overflow exists in the function decode_preR13_section_hdr in decode_r11.c | https://api.github.com/repos/LibreDWG/libredwg/issues/524/comments | 1 | 2022-11-13T04:23:10Z | 2022-11-30T12:14:12Z | https://github.com/LibreDWG/libredwg/issues/524 | 1,446,725,478 | 524 |
CVE-2022-45283 | 2022-12-06T00:15:10.257 | GPAC MP4box v2.0.0 was discovered to contain a stack overflow in the smil_parse_time_list parameter at /scenegraph/svg_attributes.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2295"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D7AEE044-50E9-4230-B492-A5FF18653115",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2295 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | GPAC-2.0.0 MP4Box: stack overflow with unlimited length and controllable content in smil_parse_time_list | https://api.github.com/repos/gpac/gpac/issues/2295/comments | 0 | 2022-10-29T18:52:22Z | 2022-11-04T08:28:14Z | https://github.com/gpac/gpac/issues/2295 | 1,428,405,742 | 2,295 |
CVE-2022-45688 | 2022-12-13T15:15:11.267 | A stack overflow in the XML.toJSONObject component of hutool-json v5.8.10 allows attackers to cause a Denial of Service (DoS) via crafted JSON or XML data. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dromara/hutool/issues/2748"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hutool:hutool:5.8.10:*:*:*:*:*:*:*",
"matchCriteriaId": "B9093201-DAC8-4158-83DA-F0DC735A7F16",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/dromara/hutool/issues/2748 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dromara",
"hutool"
] | ### 版本情况
JDK版本: openjdk_8_201
hutool版本: 5.8.10(请确保最新尝试是否还有问题)
### 问题描述(包括截图)
1. 复现代码
```
public static void main(String[] args) throws IOException {
String s="<a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a>... | Find a StackOverflowError which may lead to dos in hutool-json | https://api.github.com/repos/chinabugotech/hutool/issues/2748/comments | 7 | 2022-11-19T13:02:23Z | 2024-01-05T04:37:53Z | https://github.com/chinabugotech/hutool/issues/2748 | 1,456,460,513 | 2,748 |
CVE-2022-45689 | 2022-12-13T15:15:11.323 | hutool-json v5.8.10 was discovered to contain an out of memory error. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dromara/hutool/issues/2747"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hutool:hutool:5.8.10:*:*:*:*:*:*:*",
"matchCriteriaId": "B9093201-DAC8-4158-83DA-F0DC735A7F16",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/dromara/hutool/issues/2747 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dromara",
"hutool"
] | ### 版本情况
JDK版本: openjdk_8_201
hutool版本: 5.8.10(请确保最新尝试是否还有问题)
### 问题描述(包括截图)
1. 复现代码
```
public static void main(String[] args) {
String a="{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{'a':1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}";
JSONObject jsonObject=new JSONO... | Find a OutOfMemoryError which may lead to dos in hutool-json | https://api.github.com/repos/chinabugotech/hutool/issues/2747/comments | 3 | 2022-11-19T12:50:17Z | 2022-12-29T06:43:39Z | https://github.com/chinabugotech/hutool/issues/2747 | 1,456,453,860 | 2,747 |
CVE-2022-45690 | 2022-12-13T15:15:11.387 | A stack overflow in the org.json.JSONTokener.nextValue::JSONTokener.java component of hutool-json v5.8.10 allows attackers to cause a Denial of Service (DoS) via crafted JSON or XML data. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dromara/hutool/issues/2746"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hutool:hutool:5.8.10:*:*:*:*:*:*:*",
"matchCriteriaId": "B9093201-DAC8-4158-83DA-F0DC735A7F16",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/dromara/hutool/issues/2746 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dromara",
"hutool"
] | ### 版本情况
JDK版本: openjdk_8_201
hutool版本: 5.8.10(请确保最新尝试是否还有问题)
### 问题描述(包括截图)
1. 复现代码
```
public static void main(String[] args) {
String a="{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{... | Find a StackOverflowError which may lead to dos in hutool-json | https://api.github.com/repos/chinabugotech/hutool/issues/2746/comments | 1 | 2022-11-19T04:16:48Z | 2022-11-29T13:17:11Z | https://github.com/chinabugotech/hutool/issues/2746 | 1,456,194,214 | 2,746 |
CVE-2022-4565 | 2022-12-16T19:15:08.977 | A vulnerability classified as problematic was found in Dromara HuTool up to 5.8.10. This vulnerability affects unknown code of the file cn.hutool.core.util.ZipUtil.java. The manipulation leads to resource consumption. The attack can be initiated remotely. The exploit has been disclosed to the public and may be used. Up... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 4.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integ... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/dromara/hutool/issues/2797"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory"
],
"url": "https://vuldb.com/?id.215... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hutool:hutool:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3A7EDB42-B636-4882-A37C-98B85DF1A973",
"versionEndExcluding": null,
"versionEndIncluding": "5.8.10",
"versionStartExcludin... | [
"404"
] | 404 | https://github.com/dromara/hutool/issues/2797 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"dromara",
"hutool"
] | # 测试
JDK版本: jdk_8_291
hutool版本: 全版本
# 问题描述
## 中文
### 漏洞描述
hutool中存在zip bomb漏洞,此漏洞发生在zip解压时, zip炸弹文件中有大量刻意重复的数据,这种重复数据在压缩的时候是可以被丢弃的,这也就是压缩后的文件其实并不大的原因,但是当解压后,文件会变得非常大,通过脚本(https://github.com/CreeperKong/zipbomb-generator)
可以生成可利用的zip文件,如下图:
 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our wor... | Memory leak in gf_isom_box_parse_ex function of box_funcs.c:166:13 | https://api.github.com/repos/gpac/gpac/issues/2328/comments | 0 | 2022-11-28T06:47:39Z | 2022-11-28T10:06:52Z | https://github.com/gpac/gpac/issues/2328 | 1,465,902,126 | 2,328 |
CVE-2022-46490 | 2023-01-05T15:15:10.527 | GPAC version 2.1-DEV-rev505-gb9577e6ad-master was discovered to contain a memory leak via the afrt_box_read function at box_code_adobe.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2327"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"401"
] | 401 | https://github.com/gpac/gpac/issues/2327 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | A memory leak has occurred when running program MP4Box, this can reproduce on the lattest commit.
### Version
```
$ ./MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev505-gb9577e6ad-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our wor... | Memory leak in afrt_box_read function of box_code_adobe.c:706:35 | https://api.github.com/repos/gpac/gpac/issues/2327/comments | 0 | 2022-11-28T06:30:26Z | 2022-11-28T10:06:51Z | https://github.com/gpac/gpac/issues/2327 | 1,465,889,278 | 2,327 |
CVE-2022-47087 | 2023-01-05T15:15:10.620 | GPAC MP4box 2.1-DEV-rev574-g9d5bb184b has a Buffer overflow in gf_vvc_read_pps_bs_internal function of media_tools/av_parsers.c | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2339"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"120"
] | 120 | https://github.com/gpac/gpac/issues/2339 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | Buffer overflow in gf_vvc_read_pps_bs_internal function of media_tools/av_parsers.c | https://api.github.com/repos/gpac/gpac/issues/2339/comments | 0 | 2022-12-10T10:00:27Z | 2022-12-12T09:59:01Z | https://github.com/gpac/gpac/issues/2339 | 1,488,317,476 | 2,339 |
CVE-2022-47088 | 2023-01-05T15:15:10.663 | GPAC MP4box 2.1-DEV-rev574-g9d5bb184b is vulnerable to Buffer Overflow. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2340"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"120"
] | 120 | https://github.com/gpac/gpac/issues/2340 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | Another Buffer overflow in gf_vvc_read_pps_bs_internal function of media_tools/av_parsers.c | https://api.github.com/repos/gpac/gpac/issues/2340/comments | 0 | 2022-12-10T10:08:12Z | 2022-12-12T09:59:02Z | https://github.com/gpac/gpac/issues/2340 | 1,488,326,210 | 2,340 |
CVE-2022-47089 | 2023-01-05T15:15:10.707 | GPAC MP4box 2.1-DEV-rev574-g9d5bb184b is vulnerable to Buffer Overflow via gf_vvc_read_sps_bs_internal function of media_tools/av_parsers.c | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2338"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"120"
] | 120 | https://github.com/gpac/gpac/issues/2338 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | Buffer overflow in gf_vvc_read_sps_bs_internal function of media_tools/av_parsers.c | https://api.github.com/repos/gpac/gpac/issues/2338/comments | 0 | 2022-12-10T09:54:16Z | 2022-12-12T09:59:01Z | https://github.com/gpac/gpac/issues/2338 | 1,488,308,020 | 2,338 |
CVE-2022-47091 | 2023-01-05T15:15:10.750 | GPAC MP4box 2.1-DEV-rev574-g9d5bb184b is vulnerable to Buffer Overflow in gf_text_process_sub function of filters/load_text.c | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2343"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"120"
] | 120 | https://github.com/gpac/gpac/issues/2343 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | Buffer overflow in gf_text_process_sub function of filters/load_text.c | https://api.github.com/repos/gpac/gpac/issues/2343/comments | 0 | 2022-12-11T13:21:25Z | 2022-12-12T09:59:02Z | https://github.com/gpac/gpac/issues/2343 | 1,489,970,920 | 2,343 |
CVE-2022-47092 | 2023-01-05T15:15:10.793 | GPAC MP4box 2.1-DEV-rev574-g9d5bb184b is contains an Integer overflow vulnerability in gf_hevc_read_sps_bs_internal function of media_tools/av_parsers.c:8316 | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2347"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"190"
] | 190 | https://github.com/gpac/gpac/issues/2347 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | Integer overflow in gf_hevc_read_sps_bs_internal function of media_tools/av_parsers.c:8316 | https://api.github.com/repos/gpac/gpac/issues/2347/comments | 0 | 2022-12-11T14:02:17Z | 2022-12-12T09:59:04Z | https://github.com/gpac/gpac/issues/2347 | 1,490,026,124 | 2,347 |
CVE-2022-47093 | 2023-01-05T15:15:10.837 | GPAC MP4box 2.1-DEV-rev574-g9d5bb184b is vulnerable to heap use-after-free via filters/dmx_m2ts.c:470 in m2tsdmx_declare_pid | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2344"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"416"
] | 416 | https://github.com/gpac/gpac/issues/2344 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | heap-use-after-free filters/dmx_m2ts.c:470 in m2tsdmx_declare_pid | https://api.github.com/repos/gpac/gpac/issues/2344/comments | 0 | 2022-12-11T13:29:49Z | 2022-12-12T09:59:03Z | https://github.com/gpac/gpac/issues/2344 | 1,489,981,443 | 2,344 |
CVE-2022-47094 | 2023-01-05T15:15:10.880 | GPAC MP4box 2.1-DEV-rev574-g9d5bb184b is vulnerable to Null pointer dereference via filters/dmx_m2ts.c:343 in m2tsdmx_declare_pid | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2345"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/2345 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | Null pointer dereference filters/dmx_m2ts.c:343 in m2tsdmx_declare_pid | https://api.github.com/repos/gpac/gpac/issues/2345/comments | 0 | 2022-12-11T13:39:08Z | 2022-12-12T09:59:03Z | https://github.com/gpac/gpac/issues/2345 | 1,489,995,127 | 2,345 |
CVE-2022-47095 | 2023-01-05T15:15:10.927 | GPAC MP4box 2.1-DEV-rev574-g9d5bb184b is vulnerable to Buffer overflow in hevc_parse_vps_extension function of media_tools/av_parsers.c | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2346"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"120"
] | 120 | https://github.com/gpac/gpac/issues/2346 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | Buffer overflow in hevc_parse_vps_extension function of media_tools/av_parsers.c | https://api.github.com/repos/gpac/gpac/issues/2346/comments | 0 | 2022-12-11T13:53:19Z | 2022-12-12T09:59:03Z | https://github.com/gpac/gpac/issues/2346 | 1,490,015,617 | 2,346 |
CVE-2022-47653 | 2023-01-05T16:15:09.350 | GPAC MP4box 2.1-DEV-rev593-g007bf61a0 is vulnerable to Buffer Overflow in eac3_update_channels function of media_tools/av_parsers.c:9113 | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2349"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"120"
] | 120 | https://github.com/gpac/gpac/issues/2349 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | buffer overflow in eac3_update_channels function of media_tools/av_parsers.c:9113 | https://api.github.com/repos/gpac/gpac/issues/2349/comments | 0 | 2022-12-12T21:08:37Z | 2022-12-13T09:18:38Z | https://github.com/gpac/gpac/issues/2349 | 1,492,772,918 | 2,349 |
CVE-2022-47654 | 2023-01-05T16:15:09.587 | GPAC MP4box 2.1-DEV-rev593-g007bf61a0 is vulnerable to Buffer Overflow in gf_hevc_read_sps_bs_internal function of media_tools/av_parsers.c:8261 | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2350"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"120"
] | 120 | https://github.com/gpac/gpac/issues/2350 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | buffer overflow in gf_hevc_read_sps_bs_internal function of media_tools/av_parsers.c:8261 | https://api.github.com/repos/gpac/gpac/issues/2350/comments | 0 | 2022-12-12T21:13:33Z | 2022-12-13T09:18:38Z | https://github.com/gpac/gpac/issues/2350 | 1,492,780,269 | 2,350 |
CVE-2022-47656 | 2023-01-05T16:15:10.020 | GPAC MP4box 2.1-DEV-rev617-g85ce76efd is vulnerable to Buffer Overflow in gf_hevc_read_sps_bs_internal function of media_tools/av_parsers.c:8273 | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2353"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"120"
] | 120 | https://github.com/gpac/gpac/issues/2353 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | buffer overflow in gf_hevc_read_sps_bs_internal function of media_tools/av_parsers.c:8273 | https://api.github.com/repos/gpac/gpac/issues/2353/comments | 0 | 2022-12-16T17:03:35Z | 2022-12-16T17:36:36Z | https://github.com/gpac/gpac/issues/2353 | 1,500,560,661 | 2,353 |
CVE-2022-47657 | 2023-01-05T16:15:10.233 | GPAC MP4Box 2.1-DEV-rev644-g5c4df2a67 is vulnerable to buffer overflow in function hevc_parse_vps_extension of media_tools/av_parsers.c:7662 | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2355"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"120"
] | 120 | https://github.com/gpac/gpac/issues/2355 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | buffer overflow in function hevc_parse_vps_extension of media_tools/av_parsers.c:7662 | https://api.github.com/repos/gpac/gpac/issues/2355/comments | 0 | 2022-12-17T10:31:33Z | 2022-12-17T11:29:28Z | https://github.com/gpac/gpac/issues/2355 | 1,501,315,271 | 2,355 |
CVE-2022-47658 | 2023-01-05T16:15:10.447 | GPAC MP4Box 2.1-DEV-rev644-g5c4df2a67 is vulnerable to buffer overflow in function gf_hevc_read_vps_bs_internal of media_tools/av_parsers.c:8039 | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2356"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"120"
] | 120 | https://github.com/gpac/gpac/issues/2356 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | buffer overflow in function gf_hevc_read_vps_bs_internal of media_tools/av_parsers.c:8039 | https://api.github.com/repos/gpac/gpac/issues/2356/comments | 0 | 2022-12-17T10:31:37Z | 2022-12-17T11:29:29Z | https://github.com/gpac/gpac/issues/2356 | 1,501,315,341 | 2,356 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.