id
int64 | text
string | metadata
dict | line_start_n_end_idx
dict | quality_signals
dict | eai_taxonomy
dict | pid
string |
|---|---|---|---|---|---|---|
-9,145,764,409,956,758,000
|
Waddup!!
Checkout my daily blog where I want to have a conversation about all things technology and more. I might even throw in some pop-culture topics that includes movies and comics.
WhatsApp and Open Whisper Institutes End-To-End Encryption
File-It-Under: Encrypted messengers By: D.F.Skin Whatsapp
In the age of government intervention,snooping eyes of the NSA, its no wonder we'll ever see any form of Internet privacy. It seems like no matter app we use,be it Dropbox,Facebook, or Microsoft,they all seem to have one thing in common,they seem to enjoy handing your personal information over to the feds.
Well WhatsApp wants to do something about that,it wants to seriously protect your privacy with no trade-offs of course. On Tuesday,WhatsApp announced that it will be implementing end-to-end encryption, as part of an upgrade program to its privacy messaging service. The goal is to make it almost impossible for any,even from the United States government from reading your messages. Even the company itself (WhatsApp) won't be able encrypt your messages,nor hand over your information to law enforcement.
WhatsApp will integrate an open source software Textsecure,which is created by a privacy focused non-profit Open Whisper system. This scrambles messages with a cryptographic key which only the user can access and it will never leave your device.
I can't say how excited I am about what WhatsApp is doing,its good to see big buiness show some concern for consumer privacy.
PC Tools Weekly: Speccy
Tekspecz Holiday Shopping Guide Present: MicroSoft SurFace Pro 3
|
{
"url": "http://www.tekspecz.com/tekspecz/2014/11/19/whatsapp-and-open-whisper-institutes-end-to-end-encryption",
"source_domain": "www.tekspecz.com",
"snapshot_id": "crawl=CC-MAIN-2019-04",
"warc_metadata": {
"Content-Length": "74036",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:BS25GTBJA6ZJJMUGGN2GLRWUZXVMTCFC",
"WARC-Concurrent-To": "<urn:uuid:82ebc299-fafc-40bf-8300-d420e1358064>",
"WARC-Date": "2019-01-21T13:20:30Z",
"WARC-IP-Address": "198.185.159.144",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:PTOVHBNBO73O7EB4I5NBK5KELAGUA3N6",
"WARC-Record-ID": "<urn:uuid:a7d9c2dd-3a23-47be-80df-e9e6664117e2>",
"WARC-Target-URI": "http://www.tekspecz.com/tekspecz/2014/11/19/whatsapp-and-open-whisper-institutes-end-to-end-encryption",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:91564e6b-1277-4244-9eaa-3ba7699a2a27>"
},
"warc_info": "isPartOf: CC-MAIN-2019-04\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for January 2019\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-140-176-207.ec2.internal\r\nsoftware: Apache Nutch 1.15 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 0.11-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
9,
10,
186,
187,
246,
247,
306,
307,
616,
617,
1121,
1122,
1368,
1369,
1495,
1496,
1498,
1499,
1501,
1502,
1504,
1505,
1507,
1508,
1532,
1533
],
"line_end_idx": [
9,
10,
186,
187,
246,
247,
306,
307,
616,
617,
1121,
1122,
1368,
1369,
1495,
1496,
1498,
1499,
1501,
1502,
1504,
1505,
1507,
1508,
1532,
1533,
1597
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 1597,
"ccnet_original_nlines": 26,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.40566039085388184,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.025157229974865913,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.14779874682426453,
"rps_doc_frac_unique_words": 0.6761133670806885,
"rps_doc_mean_word_length": 5.186234951019287,
"rps_doc_num_sentences": 15,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.908838272094727,
"rps_doc_word_count": 247,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.009367680177092552,
"rps_doc_frac_chars_top_3gram": 0,
"rps_doc_frac_chars_top_4gram": 0,
"rps_doc_books_importance": -146.6840057373047,
"rps_doc_books_importance_length_correction": -133.10606384277344,
"rps_doc_openwebtext_importance": -77.99481964111328,
"rps_doc_openwebtext_importance_length_correction": -77.99481964111328,
"rps_doc_wikipedia_importance": -41.61867904663086,
"rps_doc_wikipedia_importance_length_correction": -27.91337013244629
},
"fasttext": {
"dclm": 0.020199120044708252,
"english": 0.928268551826477,
"fineweb_edu_approx": 1.3649044036865234,
"eai_general_math": 0.010221900418400764,
"eai_open_web_math": 0.013650890439748764,
"eai_web_code": 0.1024819016456604
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.82",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "353.0285",
"labels": {
"level_1": "Social sciences",
"level_2": "Public administration and Military art and science",
"level_3": "United States — Politics and government and State governments"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "1",
"label": "News/Editorial"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "16",
"label": "Personal Blog"
},
"secondary": {
"code": "13",
"label": "News (Org.)"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "6",
"label": "Not Applicable/Indeterminate"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "1",
"label": "General Audience"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-6,615,853,575,012,901,000
|
How can we create data driven framework using TestNG?
0 votes
6 days ago in Selenium by Yuvraj
14 views
1 answer to this question.
Your answer
Your name to display (optional):
Privacy: Your email address will only be used for sending these notifications.
0 votes
Hey Yuvraj, we can create a Data Driven Framework by using @DataProvider annotation in TestNG.
@DataProvider(name="getData")
public Object[][] getData(){
//Object [][] data = new Object [rowCount][colCount];
Object [][] data = new Object [2][2];
data [0][0] = "FirstId";
data [0][1] = "FirstPswd";
data[1][0] = "SecondId";
data[1][1] = "SecondPswd";
return data;
}
answered 5 days ago by Anvi
• 7,160 points
Related Questions In Selenium
0 votes
1 answer
How can we take screenshots of tests in Selenium 2 using C#
We can take screenshots using below function ...READ MORE
answered Mar 23, 2018 in Selenium by nsv999
• 5,050 points
115 views
+2 votes
1 answer
How can we handle authentication popup in Selenium WebDriver using Java
The Alert Method, authenticateUsing() lets us skip ...READ MORE
answered Apr 18, 2018 in Selenium by king_kenny
• 3,590 points
3,647 views
0 votes
1 answer
0 votes
1 answer
Finding WebDriver element with Class Name in java
The better way to handle this element ...READ MORE
answered Apr 10, 2018 in Selenium by nsv999
• 5,050 points
135 views
0 votes
1 answer
0 votes
1 answer
Geo-location microphone camera pop up
To Allow or Block the notification, access using Selenium and you have to ...READ MORE
answered May 11, 2018 in Selenium by Samarpit
• 5,130 points
526 views
0 votes
1 answer
How to use such xpath to find web elements
It's much simpler to use: #MyDiv123 > div.super or ...READ MORE
answered Jun 14, 2018 in Selenium by Samarpit
• 5,130 points
129 views
0 votes
1 answer
How can I create a POM test case in Selenium Webdriver?
Hey Akshay, follow these steps to create ...READ MORE
answered May 12 in Selenium by Anvi
• 7,160 points
22 views
0 votes
1 answer
© 2018 Brain4ce Education Solutions Pvt. Ltd. All rights Reserved.
"PMP®","PMI®", "PMI-ACP®" and "PMBOK®" are registered marks of the Project Management Institute, Inc. MongoDB®, Mongo and the leaf logo are the registered trademarks of MongoDB, Inc.
|
{
"url": "https://www.edureka.co/community/49066/how-can-we-create-data-driven-framework-using-testng",
"source_domain": "www.edureka.co",
"snapshot_id": "crawl=CC-MAIN-2019-26",
"warc_metadata": {
"Content-Length": "109406",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:G4BQYS6XOXQVYZOGJHFBUCVSYDFU6ZPM",
"WARC-Concurrent-To": "<urn:uuid:90067ea9-76cb-4c9c-a68e-c0ad5d7aaa12>",
"WARC-Date": "2019-06-18T10:37:03Z",
"WARC-IP-Address": "99.84.181.5",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:MNA5NO5FHQJZBGGOUVHQJWTJXMIVYSIQ",
"WARC-Record-ID": "<urn:uuid:007c6359-3fff-4e14-8476-dcf89ea10ba6>",
"WARC-Target-URI": "https://www.edureka.co/community/49066/how-can-we-create-data-driven-framework-using-testng",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:1f056bc6-126a-4159-9dd8-d888244e31fd>"
},
"warc_info": "isPartOf: CC-MAIN-2019-26\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for June 2019\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-166-231-116.ec2.internal\r\nsoftware: Apache Nutch 1.15 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.1-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
54,
55,
63,
96,
105,
106,
133,
134,
146,
147,
180,
259,
267,
268,
363,
364,
394,
424,
480,
520,
523,
550,
579,
582,
609,
638,
641,
656,
659,
662,
690,
705,
706,
736,
737,
745,
754,
755,
815,
816,
874,
875,
919,
934,
944,
953,
962,
963,
1035,
1036,
1100,
1101,
1149,
1164,
1176,
1184,
1193,
1201,
1210,
1211,
1261,
1262,
1313,
1314,
1358,
1373,
1383,
1391,
1400,
1408,
1417,
1418,
1456,
1457,
1544,
1545,
1591,
1606,
1616,
1624,
1633,
1634,
1677,
1678,
1742,
1743,
1789,
1804,
1814,
1822,
1831,
1832,
1888,
1889,
1943,
1944,
1980,
1995,
2004,
2012,
2021,
2022,
2089
],
"line_end_idx": [
54,
55,
63,
96,
105,
106,
133,
134,
146,
147,
180,
259,
267,
268,
363,
364,
394,
424,
480,
520,
523,
550,
579,
582,
609,
638,
641,
656,
659,
662,
690,
705,
706,
736,
737,
745,
754,
755,
815,
816,
874,
875,
919,
934,
944,
953,
962,
963,
1035,
1036,
1100,
1101,
1149,
1164,
1176,
1184,
1193,
1201,
1210,
1211,
1261,
1262,
1313,
1314,
1358,
1373,
1383,
1391,
1400,
1408,
1417,
1418,
1456,
1457,
1544,
1545,
1591,
1606,
1616,
1624,
1633,
1634,
1677,
1678,
1742,
1743,
1789,
1804,
1814,
1822,
1831,
1832,
1888,
1889,
1943,
1944,
1980,
1995,
2004,
2012,
2021,
2022,
2089,
2271
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 2271,
"ccnet_original_nlines": 103,
"rps_doc_curly_bracket": 0.0008806699770502746,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.18200409412384033,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.04089979827404022,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.3599182069301605,
"rps_doc_frac_unique_words": 0.4726775884628296,
"rps_doc_mean_word_length": 4.6366119384765625,
"rps_doc_num_sentences": 17,
"rps_doc_symbol_to_word_ratio": 0.01635991968214512,
"rps_doc_unigram_entropy": 4.74758768081665,
"rps_doc_word_count": 366,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.19799646735191345,
"rps_doc_frac_chars_dupe_6grams": 0.16735415160655975,
"rps_doc_frac_chars_dupe_7grams": 0.11667648702859879,
"rps_doc_frac_chars_dupe_8grams": 0.11667648702859879,
"rps_doc_frac_chars_dupe_9grams": 0.03653505817055702,
"rps_doc_frac_chars_top_2gram": 0.06482026726007462,
"rps_doc_frac_chars_top_3gram": 0.06364171952009201,
"rps_doc_frac_chars_top_4gram": 0.0612846203148365,
"rps_doc_books_importance": -215.5054473876953,
"rps_doc_books_importance_length_correction": -215.5054473876953,
"rps_doc_openwebtext_importance": -117.37793731689453,
"rps_doc_openwebtext_importance_length_correction": -117.37793731689453,
"rps_doc_wikipedia_importance": -130.36573791503906,
"rps_doc_wikipedia_importance_length_correction": -130.36573791503906
},
"fasttext": {
"dclm": 0.1462964415550232,
"english": 0.8178988099098206,
"fineweb_edu_approx": 1.9677313566207886,
"eai_general_math": 0.0026149700861424208,
"eai_open_web_math": 0.04265027865767479,
"eai_web_code": -0.000009180000233754981
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.133",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "23",
"label": "Tutorial"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
1,104,560,040,306,434,400
|
Question about SanDisk Sansa e250 MP3 Player
1 Answer
Volume do not work anymore
1. It seems to be in a freeze mode will not play any songs with or without the headphones
Posted by on
1 Answer
• Level 1:
An expert who has achieved level 1.
Hot-Shot:
An expert who has answered 20 questions.
Corporal:
An expert that has over 10 points.
Mayor:
An expert whose answer got voted for 2 times.
• Contributor
• 25 Answers
Re: volume do not work anymore
You need to reset the unit. Take out the 4 screws in the backplate, and disconnect the battery. Wait about 10 seconds then reattach, and replace backplate and screws. That should do it. If not, unit is bad.
Posted on Dec 26, 2007
Add Your Answer
0 characters
Uploading: 0%
my-video-file.mp4
Complete. Click "Add" to insert your video. Add
×
Loading...
Loading...
3 Points
Related Questions:
2 Answers
Sony NWZ-E438F won't play music anymore.
there is a format problem and formatting your appartus might help you
Mar 18, 2010 | Sony NWZ-E438F Digital Media Player
1 Answer
Sansa Clip Won't come from pause.
It might be a firmware issue you are having..Try going to the sandisk website to obtain a firmware update for your device..
I hope that helps
Thank you
Mar 04, 2009 | SanDisk Sansa Clip MP3 Player
1 Answer
I can't get songs to play on my sony nwz-e438f
try using a different pair of headphones and making sure the volume is turned up
Dec 29, 2008 | Sony NWZ-E438F Digital Media Player
1 Answer
Only Plays 20% of songs
This is the worst mp3 player ever invented - i have to tell you this up front. There is no driver, the company does not support the product anymore - I would return it now while you still can.
Either the device is bad, the pc port is bad, or the software is faulty. Try connecting to different usb port, then a usb port on a different pc with a compatible os. If still not recognized, then there is physical damage to player.
Try this: disconnect the player from the computer, turn it off, hold in the volume + button, and reconnect the player to the computer while holding the volume + button in. Keep holding the volume + button for an additional 5-50 seconds. Windows should eventually go into recovery mode and revive the player- it will pop up a window that says Found New Hardware Wizard.
Mar 04, 2008 | iLO (2 GB) MP3 Player
1 Answer
Problems with my sandisk sansa mp3
Do any of the songs play? It may be that the song(s) are corrupted. If this is the case, delete the songs and try to download them from somewhere else or, if you uploaded from a cd put them on again and see if they work. It also might be the jack that these speakers are plugged into. Sometimes the port for the speaker plug is made incorrectly, and the plug is too loose inside to actually connect, but tight enough to stay in. If it's a base cradle, does it work? Are you missing any batteries( if battery powered), or is the plug in the outlet right? Is the player connected properly? Is it actually FOR the player, or is it only for a certain type of player that you don't have? It by 'speaker' you mean headphones, the wires might be disconnected in some places. If that's the case, buy some $0.98 headphones from walmart and attempt it with those. Are the volume bars on the player and the speakers high enough up?
Jan 27, 2008 | SanDisk Sansa e260 MP3 Player
1 Answer
Freeze
This is the worst mp3 player ever invented - i have to tell you this up front. There is no driver, the company does not support the product anymore - I would return it now while you still can.
Either the device is bad, the pc port is bad, or the software is faulty. Try connecting to different usb port, then a usb port on a different pc with a compatible os. If still not recognized, then there is physical damage to player.
Try this: disconnect the player from the computer, turn it off, hold in the volume + button, and reconnect the player to the computer while holding the volume + button in. Keep holding the volume + button for an additional 5-50 seconds. Windows should eventually go into recovery mode and revive the player- it will pop up a window that says Found New Hardware Wizard.
Nov 27, 2007 | iLO (2 GB) MP3 Player
1 Answer
Ilo mp3 player gets stuck on first song...
Make sure the songs are in the correct format
This is the worst mp3 player ever invented - i have to tell you this up front. There is no driver, the company does not support the product anymore - I would return it now while you still can.
Either the device is bad, the pc port is bad, or the software is faulty. Try connecting to different usb port, then a usb port on a different pc with a compatible os. If still not recognized, then there is physical damage to player.
Try this: disconnect the player from the computer, turn it off, hold in the volume + button, and reconnect the player to the computer while holding the volume + button in. Keep holding the volume + button for an additional 5-50 seconds. Windows should eventually go into recovery mode and revive the player- it will pop up a window that says Found New Hardware Wizard.
Aug 07, 2007 | iLO (2 GB) MP3 Player
3 Answers
My RCA Lyra RD1072A just doesnt play songs
it freezes at the start menu just saying RCA and others times it plays a song and freezes when i turn the volume up or down can someone anyone help me please...thanx
May 16, 2007 | RCA Lyra RD1072 MP3 Player
Not finding what you are looking for?
SanDisk Sansa e250 MP3 Player Logo
Related Topics:
20 people viewed this question
Ask a Question
Usually answered in minutes!
Top SanDisk MP3 & Digital Media Players Experts
kakima
Level 3 Expert
93738 Answers
Jazz Boyce
Jazz Boyce
Level 1 Expert
728 Answers
Donald DCruz
Donald DCruz
Level 3 Expert
17129 Answers
Are you a SanDisk MP3 and Digital Media Player Expert? Answer questions, earn points and help others
Answer questions
Manuals & User Guides
Loading...
|
{
"url": "http://www.fixya.com/support/t316232-volume_not_work_anymore",
"source_domain": "www.fixya.com",
"snapshot_id": "crawl=CC-MAIN-2016-44",
"warc_metadata": {
"Content-Length": "110340",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:LNW2VPJW6Q5DJRUF4ZPU2URHOQG75HKG",
"WARC-Concurrent-To": "<urn:uuid:656ad342-49b3-4ed7-baa0-7338076ccd0c>",
"WARC-Date": "2016-10-21T18:42:07Z",
"WARC-IP-Address": "74.205.15.103",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:6A4HEC3CFPK3PDWJKFXBZVFPVSIKW22O",
"WARC-Record-ID": "<urn:uuid:067716f2-8f5c-45f9-9a54-950d1b63c7ce>",
"WARC-Target-URI": "http://www.fixya.com/support/t316232-volume_not_work_anymore",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:6fc80585-70bd-40c5-805a-15efd9d547cd>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-171-6-4.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2016-44\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web for October 2016\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
45,
46,
55,
56,
83,
84,
176,
177,
190,
191,
200,
201,
214,
215,
255,
256,
270,
271,
316,
317,
331,
332,
371,
372,
383,
384,
434,
435,
451,
466,
497,
498,
705,
706,
729,
730,
746,
747,
760,
761,
775,
776,
794,
795,
843,
844,
846,
847,
858,
869,
878,
879,
898,
899,
909,
910,
951,
952,
953,
1023,
1024,
1075,
1076,
1085,
1086,
1120,
1121,
1122,
1246,
1264,
1274,
1275,
1320,
1321,
1330,
1331,
1378,
1379,
1380,
1461,
1462,
1513,
1514,
1523,
1524,
1548,
1549,
1550,
1743,
1744,
1977,
1978,
2347,
2348,
2385,
2386,
2395,
2396,
2431,
2432,
2433,
3354,
3355,
3400,
3401,
3410,
3411,
3418,
3419,
3420,
3613,
3614,
3847,
3848,
4217,
4218,
4255,
4256,
4265,
4266,
4309,
4310,
4311,
4357,
4358,
4551,
4552,
4785,
4786,
5155,
5156,
5193,
5194,
5204,
5205,
5248,
5249,
5250,
5416,
5417,
5459,
5460,
5498,
5533,
5534,
5550,
5551,
5582,
5583,
5598,
5599,
5628,
5629,
5677,
5678,
5685,
5686,
5701,
5702,
5716,
5717,
5728,
5739,
5740,
5755,
5756,
5768,
5769,
5782,
5795,
5796,
5811,
5812,
5826,
5827,
5928,
5929,
5946,
5947,
5969,
5970
],
"line_end_idx": [
45,
46,
55,
56,
83,
84,
176,
177,
190,
191,
200,
201,
214,
215,
255,
256,
270,
271,
316,
317,
331,
332,
371,
372,
383,
384,
434,
435,
451,
466,
497,
498,
705,
706,
729,
730,
746,
747,
760,
761,
775,
776,
794,
795,
843,
844,
846,
847,
858,
869,
878,
879,
898,
899,
909,
910,
951,
952,
953,
1023,
1024,
1075,
1076,
1085,
1086,
1120,
1121,
1122,
1246,
1264,
1274,
1275,
1320,
1321,
1330,
1331,
1378,
1379,
1380,
1461,
1462,
1513,
1514,
1523,
1524,
1548,
1549,
1550,
1743,
1744,
1977,
1978,
2347,
2348,
2385,
2386,
2395,
2396,
2431,
2432,
2433,
3354,
3355,
3400,
3401,
3410,
3411,
3418,
3419,
3420,
3613,
3614,
3847,
3848,
4217,
4218,
4255,
4256,
4265,
4266,
4309,
4310,
4311,
4357,
4358,
4551,
4552,
4785,
4786,
5155,
5156,
5193,
5194,
5204,
5205,
5248,
5249,
5250,
5416,
5417,
5459,
5460,
5498,
5533,
5534,
5550,
5551,
5582,
5583,
5598,
5599,
5628,
5629,
5677,
5678,
5685,
5686,
5701,
5702,
5716,
5717,
5728,
5739,
5740,
5755,
5756,
5768,
5769,
5782,
5795,
5796,
5811,
5812,
5826,
5827,
5928,
5929,
5946,
5947,
5969,
5970,
5980
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 5980,
"ccnet_original_nlines": 181,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.374801903963089,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.02377179078757763,
"rps_doc_frac_lines_end_with_ellipsis": 0.021978020668029785,
"rps_doc_frac_no_alph_words": 0.1917591094970703,
"rps_doc_frac_unique_words": 0.30320149660110474,
"rps_doc_mean_word_length": 4.30885124206543,
"rps_doc_num_sentences": 62,
"rps_doc_symbol_to_word_ratio": 0.0039619700983166695,
"rps_doc_unigram_entropy": 5.189398765563965,
"rps_doc_word_count": 1062,
"rps_doc_frac_chars_dupe_10grams": 0.40843531489372253,
"rps_doc_frac_chars_dupe_5grams": 0.4597901999950409,
"rps_doc_frac_chars_dupe_6grams": 0.439248263835907,
"rps_doc_frac_chars_dupe_7grams": 0.4342220425605774,
"rps_doc_frac_chars_dupe_8grams": 0.40843531489372253,
"rps_doc_frac_chars_dupe_9grams": 0.40843531489372253,
"rps_doc_frac_chars_top_2gram": 0.02360139973461628,
"rps_doc_frac_chars_top_3gram": 0.029501749202609062,
"rps_doc_frac_chars_top_4gram": 0.028846150264143944,
"rps_doc_books_importance": -552.4685668945312,
"rps_doc_books_importance_length_correction": -552.4685668945312,
"rps_doc_openwebtext_importance": -334.7747802734375,
"rps_doc_openwebtext_importance_length_correction": -334.7747802734375,
"rps_doc_wikipedia_importance": -247.37014770507812,
"rps_doc_wikipedia_importance_length_correction": -247.37014770507812
},
"fasttext": {
"dclm": 0.03638625144958496,
"english": 0.9189626574516296,
"fineweb_edu_approx": 1.359325647354126,
"eai_general_math": 0.019808949902653694,
"eai_open_web_math": 0.19632309675216675,
"eai_web_code": 0.0010198400123044848
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.6",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "-1",
"labels": {
"level_1": "",
"level_2": "",
"level_3": ""
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "1",
"label": "Factual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "21",
"label": "Customer Support"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "1",
"label": "General Audience"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
2,491,256,730,507,482,000
|
How to perform scheduled notification through intune for Windows 10 devices
Question
Hi,
I have a requirement to send a notification to Windows 10 devices everyday in 6 hours interval through Intune. The popup needs to display on machine every 6 hours.
I have powershell script to display notification, but is it possible from intune to send notification / Deployed on scheduled intervals?
Let me know if there are some other options to push via intune rather than script also.
Thanks,
Dileepan A
solved 0
Dileepan Ayyanan 8 months 2 Answers 145 views Beginner 0
Answers ( 2 )
1. Toast notification or normal notification \
I’m working on a project Free Intune Training
I found something interesting while doing some testing 🙂 I have not tested this but it might help ….
You can try this for toast notification – But maybe u need to create a scheduled task and call the Extension\agentexecutor.exe
“C:\Program Files (x86)\Microsoft Intune Management Extension\agentexecutor.exe” -toast “ToastDownloadingMessage”
Best answer
Leave an answer
Sorry, you do not have a permission to answer to this question .
|
{
"url": "https://forum.howtomanagedevices.com/endpointmanager/intune/how-to-perform-scheduled-notification-through-intune-for-windows-10-devices/",
"source_domain": "forum.howtomanagedevices.com",
"snapshot_id": "crawl=CC-MAIN-2021-04",
"warc_metadata": {
"Content-Length": "116153",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:PG4DN7WQQ4RIS5NADNRF4PVWUVK2XK5F",
"WARC-Concurrent-To": "<urn:uuid:b4d51cf8-8fa6-4654-a367-bc3ddec16eb6>",
"WARC-Date": "2021-01-27T03:14:52Z",
"WARC-IP-Address": "172.67.139.142",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:TDSLWM2SOZLJRHVBPKJ4UFZVWB377VC3",
"WARC-Record-ID": "<urn:uuid:0ebc9120-2a2b-401d-97d8-00ee0cf8be04>",
"WARC-Target-URI": "https://forum.howtomanagedevices.com/endpointmanager/intune/how-to-perform-scheduled-notification-through-intune-for-windows-10-devices/",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:661b2814-a787-4fff-9cb9-2a46f400af4e>"
},
"warc_info": "isPartOf: CC-MAIN-2021-04\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for January 2021\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-33.ec2.internal\r\nsoftware: Apache Nutch 1.17 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.2-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
76,
77,
86,
87,
91,
92,
256,
257,
394,
395,
483,
484,
492,
493,
504,
505,
514,
571,
572,
586,
587,
636,
637,
687,
688,
793,
794,
925,
926,
1044,
1045,
1061,
1062,
1078,
1079
],
"line_end_idx": [
76,
77,
86,
87,
91,
92,
256,
257,
394,
395,
483,
484,
492,
493,
504,
505,
514,
571,
572,
586,
587,
636,
637,
687,
688,
793,
794,
925,
926,
1044,
1045,
1061,
1062,
1078,
1079,
1143
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 1143,
"ccnet_original_nlines": 35,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3349282443523407,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.03349281847476959,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.19617225229740143,
"rps_doc_frac_unique_words": 0.6399999856948853,
"rps_doc_mean_word_length": 5.142857074737549,
"rps_doc_num_sentences": 9,
"rps_doc_symbol_to_word_ratio": 0.004784690216183662,
"rps_doc_unigram_entropy": 4.497702598571777,
"rps_doc_word_count": 175,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.01666666939854622,
"rps_doc_frac_chars_top_3gram": 0.035555560141801834,
"rps_doc_frac_chars_top_4gram": 0,
"rps_doc_books_importance": -103.03795623779297,
"rps_doc_books_importance_length_correction": -103.03795623779297,
"rps_doc_openwebtext_importance": -37.642330169677734,
"rps_doc_openwebtext_importance_length_correction": -33.88007354736328,
"rps_doc_wikipedia_importance": -37.824134826660156,
"rps_doc_wikipedia_importance_length_correction": -37.824134826660156
},
"fasttext": {
"dclm": 0.03063357062637806,
"english": 0.8696205615997314,
"fineweb_edu_approx": 1.197433352470398,
"eai_general_math": 0.43761271238327026,
"eai_open_web_math": 0.17932504415512085,
"eai_web_code": 0.009218219667673111
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.445",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.028",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "4",
"label": "Graduate/Expert Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
1,458,345,798,752,742,400
|
1
$\begingroup$
In combinatorial optimization, there are many problems that can be formulated as either Network Flow model or Mixed Integer Programming (MIP), e.g. supply chains, transportation, and graph-base problems. Some solvers make use of logical and/or graph-base syntax to efficiently solve network problems. And then the Network Simplex method is applied.
Also, As stated in Bazaraa, M.S., Jarvis, J.J. , and Sherali, H.D.; Linear programming and network flows, 4th Edition, Hoboken, New Jersey: Wiley & Sons, Inc., 2010; page 453:
We discuss appropriate data structures that facilitate the implementation of such a graph-theoretic procedure on the computer. The overall efficiency with which such a procedure operates enables one to solve problems 200-300 times faster than with a standard simplex approach that ignores any inherent special structures other than sparsity.
Practically speaking, from the aspect of time efficiency, are there any significant differences between modelling as a mixed integer programming and modeling as a network problem? And why (other than sparsity)?
Which optimization solvers are computationally fast at solving Network problems?
$\endgroup$
1
• 1
$\begingroup$ Maybe you should read the rest of that chapter. $\endgroup$ – David Ketcheson Oct 26 '14 at 5:18
1
$\begingroup$
Practically speaking, from the aspect of time efficiency, are there any significant differences between modelling as a mixed integer programming and modeling as a network problem? And why (other than sparsity)?
Yes. The reason network simplex is faster primarily has to do with exploiting the total unimodularity of network matrices -- basically, network matrices are always structured such that their submatrices have integral inverses. This property means that for network problems, instead of having to enumerate a branch-and-bound tree to obtain an integral solution, we can invert the columns of the coefficient matrix corresponding to variables in the simplex basis and obtain an integral solution. These inversion operations are cheaper than solving the branch-and-bound tree, in that they run in worst-case polynomial time (even better than ordinary simplex, which runs in worst-case exponential time, but typically in linear time); branch-and-bound runs in worst-case exponential time, and also typically runs in exponential time for general mixed-integer programs.
Sure, sparsity is nice too, and a typical property of network problems, but the main speed gains come from being able to use regular linear algebra operations to obtain integral solutions instead of branch-and-bound, which is a glorified guess-and-check scheme.
$\endgroup$
4
• $\begingroup$ And which optimization solvers are specifically tailored to manage network flow problems? $\endgroup$ – Mohammad Namakshenas Oct 26 '14 at 8:11
• $\begingroup$ Any commercial LP solver will have solvers specialized for network flow problems expressible as LPs. The two best commercial LP solvers out there are CPLEX and Gurobi, which routinely outperform other software by at least an order of magnitude, and benchmarks are usually presented yearly at the annual INFORMS meeting to back up these performance claims. Open source solvers might also have network simplex-type algorithms. $\endgroup$ – Geoff Oxberry Oct 26 '14 at 17:32
• $\begingroup$ What I've heard (from a talk by Bob Bixby) is that current simplex implementations are about as fast, or slightly faster, than current network simplex implementations. $\endgroup$ – tmyklebu Oct 26 '14 at 22:46
• $\begingroup$ I tried to find a written reference for Bixby's talk and could not find one. Do you have a link or a paper reference? According to CPLEX's user docs, using network simplex yields speedups of up to 10-100x on network problems compared to primal or dual simplex algorithms. (According to Bixby, dual simplex is typically used.) $\endgroup$ – Geoff Oxberry Oct 27 '14 at 0:03
Your Answer
By clicking “Post Your Answer”, you agree to our terms of service, privacy policy and cookie policy
Not the answer you're looking for? Browse other questions tagged or ask your own question.
|
{
"url": "https://scicomp.stackexchange.com/questions/15984/comparison-of-the-time-efficiency-of-an-optimization-problem-formulated-as-a-net",
"source_domain": "scicomp.stackexchange.com",
"snapshot_id": "crawl=CC-MAIN-2021-21",
"warc_metadata": {
"Content-Length": "169900",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:2BF2XE6HYEP4U3ID5F3QCIDU4G2BWV4E",
"WARC-Concurrent-To": "<urn:uuid:a5899a9e-d2a3-4bd0-bc5f-efce630175a0>",
"WARC-Date": "2021-05-13T04:04:45Z",
"WARC-IP-Address": "151.101.65.69",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:DLSYX6QIR3OV7FHPTAIZJXVYTZZNE2ZH",
"WARC-Record-ID": "<urn:uuid:a7ee3f31-83f0-45db-9bf9-78c39d05bd3f>",
"WARC-Target-URI": "https://scicomp.stackexchange.com/questions/15984/comparison-of-the-time-efficiency-of-an-optimization-problem-formulated-as-a-net",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:a71a5614-1be5-4eec-868a-d7c0211643a9>"
},
"warc_info": "isPartOf: CC-MAIN-2021-21\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for May 2021\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-167.ec2.internal\r\nsoftware: Apache Nutch 1.18 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.2-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
2,
16,
17,
366,
367,
543,
544,
886,
887,
1098,
1099,
1180,
1181,
1193,
1195,
1201,
1316,
1318,
1332,
1333,
1544,
1545,
2409,
2410,
2672,
2673,
2685,
2687,
2849,
3340,
3569,
3960,
3961,
3973,
3974,
4074,
4075
],
"line_end_idx": [
2,
16,
17,
366,
367,
543,
544,
886,
887,
1098,
1099,
1180,
1181,
1193,
1195,
1201,
1316,
1318,
1332,
1333,
1544,
1545,
2409,
2410,
2672,
2673,
2685,
2687,
2849,
3340,
3569,
3960,
3961,
3973,
3974,
4074,
4075,
4165
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 4165,
"ccnet_original_nlines": 37,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3024691343307495,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.017283950001001358,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.23333333432674408,
"rps_doc_frac_unique_words": 0.480063796043396,
"rps_doc_mean_word_length": 5.323763847351074,
"rps_doc_num_sentences": 36,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 5.285826206207275,
"rps_doc_word_count": 627,
"rps_doc_frac_chars_dupe_10grams": 0.10425403714179993,
"rps_doc_frac_chars_dupe_5grams": 0.13660874962806702,
"rps_doc_frac_chars_dupe_6grams": 0.10425403714179993,
"rps_doc_frac_chars_dupe_7grams": 0.10425403714179993,
"rps_doc_frac_chars_dupe_8grams": 0.10425403714179993,
"rps_doc_frac_chars_dupe_9grams": 0.10425403714179993,
"rps_doc_frac_chars_top_2gram": 0.02246854081749916,
"rps_doc_frac_chars_top_3gram": 0.008388260379433632,
"rps_doc_frac_chars_top_4gram": 0.010784899815917015,
"rps_doc_books_importance": -374.2030029296875,
"rps_doc_books_importance_length_correction": -374.2030029296875,
"rps_doc_openwebtext_importance": -196.92308044433594,
"rps_doc_openwebtext_importance_length_correction": -196.92308044433594,
"rps_doc_wikipedia_importance": -131.171875,
"rps_doc_wikipedia_importance_length_correction": -131.171875
},
"fasttext": {
"dclm": 0.07685589790344238,
"english": 0.9202536344528198,
"fineweb_edu_approx": 2.0361945629119873,
"eai_general_math": 0.8452682495117188,
"eai_open_web_math": 0.6763578653335571,
"eai_web_code": 0.013381180353462696
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "519.7",
"labels": {
"level_1": "Science and Natural history",
"level_2": "Mathematics",
"level_3": "Probabilities; or, Mathematical statistics"
}
},
"secondary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "4",
"label": "Analyze"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "1",
"label": "Leftover HTML"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "4",
"label": "Advanced Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "4",
"label": "Graduate/Expert Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-1,565,266,622,062,209,300
|
Ubuntu 安装无线网卡
By | 2018-11-27
Ubuntu 8.04 也适用
Configuration/installation of ndiswrapper under Ubuntu 7.04
NOTE:’ More general information about ndiswrapper on Ubuntu can be found [here].
1. ndiswrapper installation
From a command line, run the following command:
sudo apt-get install ndiswrapper-common ndisgtk
2. Disable the “bcm43xx” driver on your system
Run the following command at a command prompt:
echo ‘blacklist bcm43xx’ | sudo tee -a /etc/modprobe.d/blacklist
3. Download the Windows driver for your card
Go to support.dell.com and download the appropriate Windows driver for your TrueMobile card (should be something like R123456.EXE). Save this in the /tmp directory
cd into the /tmp directory, and unzip the Windows driver package
cd /tmp
unzip http://ftp.us.dell.com/network/R174291.exe
(or whatever the name of the download is)
4. Install the Windows driver with ndiswrapper
Run the following command to load the driver
sudo ndiswrapper -i /tmp/DRIVER/bcmwl5.inf
Verify that the driver has been loaded
ndiswrapper -l
The output of this command should look like the following if it is loaded correctly
Installed ndis drivers:
{name of driver} driver present, hardware present
or
{name of driver} : driver installed
device ({Chipset ID}) present
5. Load the ndiswrapper module
You now need to load the ndiswrapper module. Complete the following steps at a command prompt:
sudo depmod -a
sudo modprobe ndiswrapper
You may also want to check for error messages:
tail /var/log/messages
Assuming there are no errors, you should then try to bring up the network connection.
6. Configure network manager to use your wireless card
1. Open the Networking Admin tool (System | Administration | Networking), select the Wireless connection and click Properties, ensure the Enable roaming mode checkbox is ticked.
2. Click the Network Manager icon (computers icon in the top right corner of system tray), your network ESSID should be shown in the drop-down list. Select your network by clicking on it.
3. If the Network requires any further configuration (eg WEP key), a dialog should appear, select the correct settings and paste in your key.
7. Set the ndiswrapper module to automatically load at boot
If you are using the network manager applet to configure Wireless Network, ndiswrapper will not be started by the network manager alias setting. You must configure your system to load the ndiswrapper module at system startup. To do this, edit /etc/modules file to add an entry for ndiswrapper at the end of the file.
gksudo gedit /etc/modules
then add the word ndiswrapper to the end of this file and save it.
Your wireless should now work on subsequent reboots.
發佈留言
|
{
"url": "https://www.iokiok.tk/2018/11/27/ubuntu-%E5%AE%89%E8%A3%85%E6%97%A0%E7%BA%BF%E7%BD%91%E5%8D%A1/",
"source_domain": "www.iokiok.tk",
"snapshot_id": "crawl=CC-MAIN-2022-40",
"warc_metadata": {
"Content-Length": "38151",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:ZHQHW3F3C6TQGHD6MIKOOGAVBIXKYXGD",
"WARC-Concurrent-To": "<urn:uuid:ac3198a6-8f56-4f95-9e54-7ddea5ef4c4c>",
"WARC-Date": "2022-10-06T18:05:26Z",
"WARC-IP-Address": "104.21.78.130",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:FX4RAQDUP5SG2TM5B5SKQPV3RWGTIQKA",
"WARC-Record-ID": "<urn:uuid:c0beb3ef-f236-49e2-881e-4258fd17e3fe>",
"WARC-Target-URI": "https://www.iokiok.tk/2018/11/27/ubuntu-%E5%AE%89%E8%A3%85%E6%97%A0%E7%BA%BF%E7%BD%91%E5%8D%A1/",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:43d3816b-5a47-4dfc-ac9f-a1cb43a8b41f>"
},
"warc_info": "isPartOf: CC-MAIN-2022-40\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for September/October 2022\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-12\r\nsoftware: Apache Nutch 1.19 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.4-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
14,
15,
31,
32,
48,
49,
109,
110,
111,
192,
220,
221,
269,
270,
318,
319,
366,
367,
414,
415,
480,
481,
526,
527,
691,
756,
757,
765,
814,
856,
857,
904,
905,
950,
951,
994,
995,
1034,
1035,
1050,
1051,
1135,
1136,
1160,
1210,
1211,
1214,
1215,
1251,
1281,
1282,
1313,
1314,
1409,
1410,
1425,
1451,
1452,
1499,
1500,
1523,
1524,
1610,
1665,
1666,
1844,
2032,
2174,
2175,
2235,
2236,
2553,
2554,
2580,
2581,
2648,
2649,
2702,
2703
],
"line_end_idx": [
14,
15,
31,
32,
48,
49,
109,
110,
111,
192,
220,
221,
269,
270,
318,
319,
366,
367,
414,
415,
480,
481,
526,
527,
691,
756,
757,
765,
814,
856,
857,
904,
905,
950,
951,
994,
995,
1034,
1035,
1050,
1051,
1135,
1136,
1160,
1210,
1211,
1214,
1215,
1251,
1281,
1282,
1313,
1314,
1409,
1410,
1425,
1451,
1452,
1499,
1500,
1523,
1524,
1610,
1665,
1666,
1844,
2032,
2174,
2175,
2235,
2236,
2553,
2554,
2580,
2581,
2648,
2649,
2702,
2703,
2707
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 2707,
"ccnet_original_nlines": 79,
"rps_doc_curly_bracket": 0.0022164799738675356,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.32477062940597534,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.014678900130093098,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.2238532155752182,
"rps_doc_frac_unique_words": 0.4795180559158325,
"rps_doc_mean_word_length": 5.171084403991699,
"rps_doc_num_sentences": 35,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.820190906524658,
"rps_doc_word_count": 415,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.02423113025724888,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.027958989143371582,
"rps_doc_frac_chars_top_3gram": 0.037278659641742706,
"rps_doc_frac_chars_top_4gram": 0.03075489029288292,
"rps_doc_books_importance": -246.0589599609375,
"rps_doc_books_importance_length_correction": -246.0589599609375,
"rps_doc_openwebtext_importance": -144.70599365234375,
"rps_doc_openwebtext_importance_length_correction": -144.70599365234375,
"rps_doc_wikipedia_importance": -86.886962890625,
"rps_doc_wikipedia_importance_length_correction": -86.886962890625
},
"fasttext": {
"dclm": 0.056449711322784424,
"english": 0.7614063620567322,
"fineweb_edu_approx": 2.0206942558288574,
"eai_general_math": 0.6648562550544739,
"eai_open_web_math": 0.13815581798553467,
"eai_web_code": 0.23407107591629028
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.02854",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "005.456",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "2",
"label": "Click Here References"
}
},
"document_type_v2": {
"primary": {
"code": "23",
"label": "Tutorial"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
2,001,945,595,348,057,900
|
[Bug 604810] Gstreamer Related functions crash when a XMLSerializer has been created
GStreamer (GNOME Bugzilla) bugzilla at gnome.org
Fri Feb 27 04:08:55 PST 2015
https://bugzilla.gnome.org/show_bug.cgi?id=604810
Domingo López <dlopez at visual-tools.com> changed:
What |Removed |Added
----------------------------------------------------------------------------
CC| |dlopez at visual-tools.com
--- Comment #13 from Domingo López <dlopez at visual-tools.com> ---
Hi!
I know that it is so long since this bug was marked as resolved but I have an
issue related with it and I have not found any other place to ask for.
Applying this patch I have achieved to use XmlSerializer and GStreamer inside
my project without problems... Thanks!
However, I still appreciate an issue about this code. Some exceptions (always
the same) are launched during the loading of GStreamer binding assemblies:
"System.NotSupportedException: The invoked member is not supported in a dynamic
assembly"
The exception seems to be thrown at the line:
if (asm.Location != String.Empty) {...
(I guess the call to "Location" member has the fault)
And finally, the (dynamic?) assembly ("asm" variable) that origins everything
is:
{Microsoft.GeneratedCode, Version=1.0.0.0, Culture=neutral,
PublicKeyToken=null}
I know that all the exceptions thrown here are ignored by this code:
...
} catch (Exception) {
/* Failure to load a referenced assembly is not an error */
}
But I would like to better understand the problem and till now I have not found
anything out there. Some questions:
What is the assembly "Microsoft.GeneratedCode" and which is its relationship
with the "XmlSerializer"? Is it a dynamic assembly? A dynamic assembly is the
same than a "referenced assembly"? Which is its mission here?
Some help would be very appreciated. Thanks a lot in advance.
Domingo.
--
You are receiving this mail because:
You are the QA Contact for the bug.
You are the assignee for the bug.
More information about the gstreamer-bugs mailing list
|
{
"url": "https://lists.freedesktop.org/archives/gstreamer-bugs/2015-February/142450.html",
"source_domain": "lists.freedesktop.org",
"snapshot_id": "crawl=CC-MAIN-2019-43",
"warc_metadata": {
"Content-Length": "5530",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:HRVR5NOIC5AD2W3ZOUGL6H6XD7SL5PCE",
"WARC-Concurrent-To": "<urn:uuid:3b48dc16-e63a-4260-9521-590fadf5db06>",
"WARC-Date": "2019-10-17T21:42:30Z",
"WARC-IP-Address": "131.252.210.177",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:INQNRSF7XDTNRZ6C3YJNTXAMROUQGKZ3",
"WARC-Record-ID": "<urn:uuid:104d1837-2f42-4d70-9ee3-f617637f9e7e>",
"WARC-Target-URI": "https://lists.freedesktop.org/archives/gstreamer-bugs/2015-February/142450.html",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:7505b8a2-cbaa-452c-adb3-7df9ebb4f933>"
},
"warc_info": "isPartOf: CC-MAIN-2019-43\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for October 2019\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-180.ec2.internal\r\nsoftware: Apache Nutch 1.16 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.1-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
85,
86,
135,
164,
165,
166,
216,
217,
269,
270,
325,
402,
478,
479,
547,
551,
552,
630,
701,
702,
780,
819,
820,
898,
973,
974,
1054,
1064,
1065,
1111,
1112,
1151,
1152,
1206,
1207,
1285,
1289,
1290,
1350,
1371,
1372,
1441,
1442,
1446,
1468,
1530,
1532,
1533,
1613,
1649,
1650,
1727,
1805,
1867,
1868,
1930,
1931,
1940,
1941,
1945,
1982,
2018,
2052,
2053,
2054
],
"line_end_idx": [
85,
86,
135,
164,
165,
166,
216,
217,
269,
270,
325,
402,
478,
479,
547,
551,
552,
630,
701,
702,
780,
819,
820,
898,
973,
974,
1054,
1064,
1065,
1111,
1112,
1151,
1152,
1206,
1207,
1285,
1289,
1290,
1350,
1371,
1372,
1441,
1442,
1446,
1468,
1530,
1532,
1533,
1613,
1649,
1650,
1727,
1805,
1867,
1868,
1930,
1931,
1940,
1941,
1945,
1982,
2018,
2052,
2053,
2054,
2108
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 2108,
"ccnet_original_nlines": 65,
"rps_doc_curly_bracket": 0.0028462999034672976,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.31980907917022705,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.03341288864612579,
"rps_doc_frac_lines_end_with_ellipsis": 0.030303029343485832,
"rps_doc_frac_no_alph_words": 0.276849627494812,
"rps_doc_frac_unique_words": 0.5574913024902344,
"rps_doc_mean_word_length": 5.247386932373047,
"rps_doc_num_sentences": 36,
"rps_doc_symbol_to_word_ratio": 0.00954653974622488,
"rps_doc_unigram_entropy": 4.75883150100708,
"rps_doc_word_count": 287,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.04648074135184288,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.013280210085213184,
"rps_doc_frac_chars_top_3gram": 0.0438246987760067,
"rps_doc_frac_chars_top_4gram": 0.027888450771570206,
"rps_doc_books_importance": -160.05357360839844,
"rps_doc_books_importance_length_correction": -160.05357360839844,
"rps_doc_openwebtext_importance": -118.10276794433594,
"rps_doc_openwebtext_importance_length_correction": -118.10276794433594,
"rps_doc_wikipedia_importance": -78.19355773925781,
"rps_doc_wikipedia_importance_length_correction": -78.19355773925781
},
"fasttext": {
"dclm": 0.047242820262908936,
"english": 0.9031131863594055,
"fineweb_edu_approx": 1.0556069612503052,
"eai_general_math": 0.0574948787689209,
"eai_open_web_math": 0.11951900273561478,
"eai_web_code": 0.1299903392791748
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.4",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.02",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "4",
"label": "Analyze"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "21",
"label": "Customer Support"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "4",
"label": "Graduate/Expert Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
2,875,892,918,873,874,400
|
[PATCH v5 2/7] models: Add 'Series' model and related models
Stephen Finucane stephen at that.guru
Mon Oct 10 09:25:16 AEDT 2016
Add a series model. This model is intentionally very minimal to allow
as much dynaminism as possible. It is expected that patches will be
migrated between series as new data is provided.
Signed-off-by: Stephen Finucane <stephen at that.guru>
---
v5:
- Store cover letter name in SeriesRevision.name field
- Add warning about using the 'Patch.series' property, which causes a
new query each time
v4:
- Convert 'SeriesRevision'-'Patch' relationship from one-to-many to
many-to-many
- Remove 'Series' model, which is not used yet (revisioning is a
minefield that's being addressed separately)
- Add 'name' field to 'SeriesRevision'
v2:
- Resolve issue with REST API (Andrew Donnellan)
- Use more meaningful names for untitled series (Andrew Donnellan)
v1:
- Rename 'SeriesGroup' to 'Series'
- Rename 'Series' to 'SeriesRevision'
---
patchwork/admin.py | 67 ++++++++++-
patchwork/migrations/0014_add_series_models.py | 67 +++++++++++
patchwork/models.py | 158 +++++++++++++++++++++++--
3 files changed, 274 insertions(+), 18 deletions(-)
create mode 100644 patchwork/migrations/0014_add_series_models.py
diff --git a/patchwork/admin.py b/patchwork/admin.py
index 85ffecf..49bd55b 100644
--- a/patchwork/admin.py
+++ b/patchwork/admin.py
@@ -21,9 +21,20 @@ from __future__ import absolute_import
from django.contrib import admin
-from patchwork.models import (Project, Person, UserProfile, State, Submission,
- Patch, CoverLetter, Comment, Bundle, Tag, Check,
- DelegationRule)
+from patchwork.models import Bundle
+from patchwork.models import Check
+from patchwork.models import Comment
+from patchwork.models import CoverLetter
+from patchwork.models import DelegationRule
+from patchwork.models import Patch
+from patchwork.models import Person
+from patchwork.models import Project
+from patchwork.models import SeriesReference
+from patchwork.models import SeriesRevision
+from patchwork.models import State
+from patchwork.models import Submission
+from patchwork.models import Tag
+from patchwork.models import UserProfile
class DelegationRuleInline(admin.TabularInline):
@@ -68,13 +79,22 @@ class SubmissionAdmin(admin.ModelAdmin):
search_fields = ('name', 'submitter__name', 'submitter__email')
date_hierarchy = 'date'
admin.site.register(Submission, SubmissionAdmin)
-admin.site.register(CoverLetter, SubmissionAdmin)
+
+
+class CoverLetterAdmin(admin.ModelAdmin):
+ list_display = ('name', 'submitter', 'project', 'date', 'series')
+ list_filter = ('project', )
+ readonly_fields = ('series', )
+ search_fields = ('name', 'submitter__name', 'submitter__email')
+ date_hierarchy = 'date'
+admin.site.register(CoverLetter, CoverLetterAdmin)
class PatchAdmin(admin.ModelAdmin):
list_display = ('name', 'submitter', 'project', 'state', 'date',
- 'archived', 'is_pull_request')
+ 'archived', 'is_pull_request', 'series')
list_filter = ('project', 'state', 'archived')
+ readonly_fields = ('series', )
search_fields = ('name', 'submitter__name', 'submitter__email')
date_hierarchy = 'date'
@@ -94,6 +114,43 @@ class CommentAdmin(admin.ModelAdmin):
admin.site.register(Comment, CommentAdmin)
+class PatchInline(admin.StackedInline):
+ model = SeriesRevision.patches.through
+ extra = 0
+
+
+class SeriesRevisionAdmin(admin.ModelAdmin):
+ list_display = ('name', 'date', 'submitter', 'version', 'total',
+ 'actual_total', 'complete')
+ readonly_fields = ('actual_total', 'complete')
+ search_fields = ('submitter_name', 'submitter_email')
+ exclude = ('patches', )
+ inlines = (PatchInline, )
+
+ def complete(self, series):
+ return series.complete
+ complete.boolean = True
+admin.site.register(SeriesRevision, SeriesRevisionAdmin)
+
+
+class SeriesRevisionInline(admin.StackedInline):
+ model = SeriesRevision
+ readonly_fields = ('date', 'submitter', 'version', 'total',
+ 'actual_total', 'complete')
+ ordering = ('-date', )
+ show_change_link = True
+ extra = 0
+
+ def complete(self, series):
+ return series.complete
+ complete.boolean = True
+
+
+class SeriesReferenceAdmin(admin.ModelAdmin):
+ model = SeriesReference
+admin.site.register(SeriesReference, SeriesReferenceAdmin)
+
+
class CheckAdmin(admin.ModelAdmin):
list_display = ('patch', 'user', 'state', 'target_url',
'description', 'context')
diff --git a/patchwork/migrations/0014_add_series_models.py b/patchwork/migrations/0014_add_series_models.py
new file mode 100644
index 0000000..8d0fffa
--- /dev/null
+++ b/patchwork/migrations/0014_add_series_models.py
@@ -0,0 +1,67 @@
+# -*- coding: utf-8 -*-
+from __future__ import unicode_literals
+
+from django.db import migrations, models
+import django.db.models.deletion
+
+
+class Migration(migrations.Migration):
+
+ dependencies = [
+ ('patchwork', '0013_slug_check_context'),
+ ]
+
+ operations = [
+ migrations.CreateModel(
+ name='SeriesReference',
+ fields=[
+ ('id', models.AutoField(auto_created=True, primary_key=True, serialize=False, verbose_name='ID')),
+ ('msgid', models.CharField(max_length=255, unique=True)),
+ ],
+ ),
+ migrations.CreateModel(
+ name='SeriesRevision',
+ fields=[
+ ('id', models.AutoField(auto_created=True, primary_key=True, serialize=False, verbose_name='ID')),
+ ('name', models.CharField(blank=True, help_text=b'An optional name to associate with the series, e.g. "John\'s PCI series".', max_length=255, null=True)),
+ ('date', models.DateTimeField()),
+ ('version', models.IntegerField(default=1, help_text=b'Version of series revision as indicated by the subject prefix(es)')),
+ ('total', models.IntegerField(help_text=b'Number of patches in series as indicated by the subject prefix(es)')),
+ ('cover_letter', models.ForeignKey(blank=True, null=True, on_delete=django.db.models.deletion.CASCADE, related_name='series_revisions', to='patchwork.CoverLetter')),
+ ],
+ options={
+ 'ordering': ('date',),
+ },
+ ),
+ migrations.CreateModel(
+ name='SeriesRevisionPatch',
+ fields=[
+ ('id', models.AutoField(auto_created=True, primary_key=True, serialize=False, verbose_name='ID')),
+ ('number', models.PositiveSmallIntegerField(help_text=b'The number assigned to this patch in the series revision')),
+ ('patch', models.ForeignKey(on_delete=django.db.models.deletion.CASCADE, to='patchwork.Patch')),
+ ('revision', models.ForeignKey(on_delete=django.db.models.deletion.CASCADE, to='patchwork.SeriesRevision')),
+ ],
+ options={
+ 'ordering': ['number'],
+ },
+ ),
+ migrations.AddField(
+ model_name='seriesrevision',
+ name='patches',
+ field=models.ManyToManyField(related_name='series_revisions', related_query_name=b'series_revision', through='patchwork.SeriesRevisionPatch', to='patchwork.Patch'),
+ ),
+ migrations.AddField(
+ model_name='seriesrevision',
+ name='submitter',
+ field=models.ForeignKey(on_delete=django.db.models.deletion.CASCADE, to='patchwork.Person'),
+ ),
+ migrations.AddField(
+ model_name='seriesreference',
+ name='series',
+ field=models.ForeignKey(on_delete=django.db.models.deletion.CASCADE, related_name='references', related_query_name=b'reference', to='patchwork.SeriesRevision'),
+ ),
+ migrations.AlterUniqueTogether(
+ name='seriesrevisionpatch',
+ unique_together=set([('revision', 'number'), ('revision', 'patch')]),
+ ),
+ ]
diff --git a/patchwork/models.py b/patchwork/models.py
index 28e9861..4a55c1d 100644
--- a/patchwork/models.py
+++ b/patchwork/models.py
@@ -293,7 +293,7 @@ class EmailMixin(models.Model):
@python_2_unicode_compatible
class Submission(EmailMixin, models.Model):
- # parent
+ # parents
project = models.ForeignKey(Project)
@@ -318,11 +318,27 @@ class Submission(EmailMixin, models.Model):
class CoverLetter(Submission):
- pass
+
+ @property
+ def series(self):
+ """Get a simple series reference.
+
+ Return the last series revision that (ordered by date) that
+ this submission is a member of.
+
+ .. warning::
+ Be judicious in your use of this. For example, do not use it
+ in list templates as doing so will result in a new query for
+ each item in the list.
+ """
+ # NOTE(stephenfin): We don't use 'latest()' here, as this can raise an
+ # exception if no series revisions exist
+ return self.series_revisions.order_by('-date').first()
@python_2_unicode_compatible
class Patch(Submission):
+
# patch metadata
diff = models.TextField(null=True, blank=True)
@@ -419,17 +435,6 @@ class Patch(Submission):
for tag in tags:
self._set_tag(tag, counter[tag])
- def save(self, *args, **kwargs):
- if not hasattr(self, 'state') or not self.state:
- self.state = get_default_initial_patch_state()
-
- if self.hash is None and self.diff is not None:
- self.hash = self.hash_diff(self.diff).hexdigest()
-
- super(Patch, self).save(**kwargs)
-
- self.refresh_tag_counts()
-
def is_editable(self, user):
if not user.is_authenticated():
return False
@@ -440,6 +445,22 @@ class Patch(Submission):
return self.project.is_editable(user)
@property
+ def series(self):
+ """Get a simple series reference.
+
+ Return the last series revision that (ordered by date) that
+ this submission is a member of.
+
+ .. warning::
+ Be judicious in your use of this. For example, do not use it
+ in list templates as doing so will result in a new query for
+ each item in the list.
+ """
+ # NOTE(stephenfin): We don't use 'latest()' here, as this can raise an
+ # exception if no series revisions exist
+ return self.series_revisions.order_by('-date').first()
+
+ @property
def filename(self):
fname_re = re.compile(r'[^-_A-Za-z0-9\.]+')
str = fname_re.sub('-', self.name)
@@ -546,6 +567,17 @@ class Patch(Submission):
def __str__(self):
return self.name
+ def save(self, *args, **kwargs):
+ if not hasattr(self, 'state') or not self.state:
+ self.state = get_default_initial_patch_state()
+
+ if self.hash is None and self.diff is not None:
+ self.hash = self.hash_diff(self.diff).hexdigest()
+
+ super(Patch, self).save(**kwargs)
+
+ self.refresh_tag_counts()
+
class Meta:
verbose_name_plural = 'Patches'
@@ -569,6 +601,106 @@ class Comment(EmailMixin, models.Model):
unique_together = [('msgid', 'submission')]
+ at python_2_unicode_compatible
+class SeriesRevision(models.Model):
+ """An individual revision of a series."""
+
+ # content
+ cover_letter = models.ForeignKey(CoverLetter,
+ related_name='series_revisions',
+ null=True, blank=True)
+ patches = models.ManyToManyField(Patch, through='SeriesRevisionPatch',
+ related_name='series_revisions',
+ related_query_name='series_revision')
+
+ # metadata
+ name = models.CharField(max_length=255, blank=True, null=True,
+ help_text='An optional name to associate with '
+ 'the series, e.g. "John\'s PCI series".')
+ date = models.DateTimeField()
+ submitter = models.ForeignKey(Person)
+ version = models.IntegerField(default=1,
+ help_text='Version of series revision as '
+ 'indicated by the subject prefix(es)')
+ total = models.IntegerField(help_text='Number of patches in series as '
+ 'indicated by the subject prefix(es)')
+
+ @property
+ def actual_total(self):
+ return self.patches.count()
+
+ @property
+ def complete(self):
+ return self.total == self.actual_total
+
+ def add_cover_letter(self, cover):
+ """Add a cover letter to the series revision.
+
+ Helper method so we can use the same pattern to add both
+ patches and cover letters.
+ """
+ self.cover_letter = cover
+
+ if not self.name: # don't override user-defined names
+ self.name = cover.name.split(']')[-1]
+
+ self.save()
+
+ def add_patch(self, patch, number):
+ """Add a patch to the series revision."""
+ # see if the patch is already in this series
+ if SeriesRevisionPatch.objects.filter(revision=self,
+ patch=patch).count():
+ return
+
+ return SeriesRevisionPatch.objects.create(patch=patch,
+ revision=self,
+ number=number)
+
+ def __str__(self):
+ return self.name if self.name else 'Untitled series #%d' % self.id
+
+ class Meta:
+ ordering = ('date',)
+
+
+ at python_2_unicode_compatible
+class SeriesRevisionPatch(models.Model):
+ """A patch in a series revision.
+
+ Patches can belong to many series revisions. This allows for things
+ like auto-completion of partial series.
+ """
+ patch = models.ForeignKey(Patch)
+ revision = models.ForeignKey(SeriesRevision)
+ number = models.PositiveSmallIntegerField(
+ help_text='The number assigned to this patch in the series revision')
+
+ def __str__(self):
+ return self.patch.name
+
+ class Meta:
+ unique_together = [('revision', 'patch'), ('revision', 'number')]
+ ordering = ['number']
+
+
+ at python_2_unicode_compatible
+class SeriesReference(models.Model):
+ """A reference found in a series.
+
+ Message IDs should be created for all patches in a series,
+ including those of patches that have not yet been received. This is
+ required to handle the case whereby one or more patches are
+ received before the cover letter.
+ """
+ series = models.ForeignKey(SeriesRevision, related_name='references',
+ related_query_name='reference')
+ msgid = models.CharField(max_length=255, unique=True)
+
+ def __str__(self):
+ return self.msgid
+
+
class Bundle(models.Model):
owner = models.ForeignKey(User)
project = models.ForeignKey(Project)
--
2.7.4
More information about the Patchwork mailing list
|
{
"url": "https://lists.ozlabs.org/pipermail/patchwork/2016-October/003506.html",
"source_domain": "lists.ozlabs.org",
"snapshot_id": "CC-MAIN-2023-40",
"warc_metadata": {
"Content-Length": "18735",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:LQVUG5AZF2QU33MDLIZH5KNND2CAULFI",
"WARC-Concurrent-To": "<urn:uuid:bbbac2a0-c941-4baf-a141-c6099c8867f3>",
"WARC-Date": "2023-09-26T00:24:00Z",
"WARC-IP-Address": "112.213.38.117",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:QBXGLID23SCBSXQHNHTWADD6EAT5KEEZ",
"WARC-Record-ID": "<urn:uuid:b843de36-d973-4adc-846f-609370097317>",
"WARC-Target-URI": "https://lists.ozlabs.org/pipermail/patchwork/2016-October/003506.html",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:5263108e-6985-4ff9-b55a-b08035bea079>"
},
"warc_info": "isPartOf: CC-MAIN-2023-40\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for September/October 2023\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-67\r\nsoftware: Apache Nutch 1.19 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.5-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
61,
62,
100,
130,
131,
132,
202,
270,
319,
320,
375,
379,
383,
438,
508,
530,
534,
602,
617,
682,
729,
768,
772,
821,
888,
892,
927,
965,
969,
1035,
1101,
1181,
1234,
1301,
1302,
1355,
1385,
1410,
1435,
1493,
1495,
1529,
1531,
1611,
1691,
1738,
1775,
1811,
1849,
1891,
1936,
1972,
2009,
2047,
2093,
2138,
2174,
2215,
2249,
2291,
2293,
2295,
2345,
2406,
2475,
2504,
2554,
2605,
2607,
2609,
2652,
2723,
2756,
2792,
2861,
2890,
2942,
2944,
2946,
2983,
3053,
3105,
3167,
3219,
3255,
3324,
3353,
3355,
3413,
3457,
3459,
3461,
3502,
3546,
3561,
3563,
3565,
3611,
3681,
3730,
3782,
3841,
3870,
3901,
3903,
3936,
3968,
3997,
4055,
4057,
4059,
4109,
4137,
4202,
4254,
4282,
4311,
4326,
4328,
4361,
4393,
4422,
4424,
4426,
4473,
4502,
4562,
4564,
4566,
4603,
4664,
4711,
4820,
4841,
4864,
4878,
4931,
4948,
4973,
5014,
5016,
5058,
5092,
5094,
5096,
5136,
5138,
5160,
5211,
5218,
5220,
5240,
5273,
5310,
5332,
5448,
5523,
5539,
5551,
5584,
5620,
5642,
5758,
5930,
5981,
6123,
6253,
6436,
6452,
6475,
6515,
6531,
6543,
6576,
6617,
6639,
6755,
6889,
7003,
7129,
7145,
7168,
7209,
7225,
7237,
7267,
7309,
7338,
7516,
7528,
7558,
7600,
7631,
7737,
7749,
7779,
7822,
7850,
8024,
8036,
8077,
8118,
8201,
8213,
8220,
8275,
8305,
8331,
8357,
8409,
8411,
8441,
8486,
8500,
8515,
8517,
8559,
8561,
8627,
8629,
8631,
8663,
8673,
8675,
8690,
8713,
8756,
8758,
8827,
8868,
8870,
8892,
8964,
9036,
9070,
9083,
9163,
9213,
9277,
9279,
9281,
9311,
9337,
9339,
9361,
9363,
9415,
9461,
9487,
9533,
9535,
9573,
9631,
9691,
9693,
9750,
9813,
9815,
9858,
9860,
9895,
9897,
9931,
9972,
9998,
10044,
10091,
10093,
10108,
10131,
10174,
10176,
10245,
10286,
10288,
10310,
10382,
10454,
10488,
10501,
10581,
10631,
10695,
10697,
10712,
10737,
10790,
10834,
10880,
10904,
10930,
10932,
10970,
11028,
11088,
11090,
11147,
11210,
11212,
11255,
11257,
11292,
11294,
11311,
11352,
11354,
11417,
11470,
11472,
11474,
11507,
11544,
11591,
11593,
11608,
11659,
11730,
11791,
11867,
11938,
12014,
12016,
12032,
12100,
12177,
12248,
12283,
12326,
12372,
12450,
12524,
12601,
12673,
12675,
12690,
12719,
12756,
12758,
12773,
12798,
12846,
12848,
12888,
12943,
12945,
13011,
13047,
13060,
13095,
13097,
13161,
13212,
13214,
13235,
13237,
13278,
13329,
13383,
13445,
13514,
13534,
13536,
13600,
13666,
13732,
13734,
13758,
13834,
13836,
13853,
13883,
13885,
13887,
13920,
13962,
14000,
14002,
14075,
14120,
14129,
14167,
14217,
14265,
14344,
14346,
14370,
14402,
14404,
14421,
14496,
14527,
14529,
14531,
14564,
14602,
14641,
14643,
14707,
14780,
14845,
14884,
14893,
14968,
15032,
15091,
15093,
15117,
15144,
15146,
15148,
15177,
15214,
15256,
15260,
15266,
15267,
15268,
15269
],
"line_end_idx": [
61,
62,
100,
130,
131,
132,
202,
270,
319,
320,
375,
379,
383,
438,
508,
530,
534,
602,
617,
682,
729,
768,
772,
821,
888,
892,
927,
965,
969,
1035,
1101,
1181,
1234,
1301,
1302,
1355,
1385,
1410,
1435,
1493,
1495,
1529,
1531,
1611,
1691,
1738,
1775,
1811,
1849,
1891,
1936,
1972,
2009,
2047,
2093,
2138,
2174,
2215,
2249,
2291,
2293,
2295,
2345,
2406,
2475,
2504,
2554,
2605,
2607,
2609,
2652,
2723,
2756,
2792,
2861,
2890,
2942,
2944,
2946,
2983,
3053,
3105,
3167,
3219,
3255,
3324,
3353,
3355,
3413,
3457,
3459,
3461,
3502,
3546,
3561,
3563,
3565,
3611,
3681,
3730,
3782,
3841,
3870,
3901,
3903,
3936,
3968,
3997,
4055,
4057,
4059,
4109,
4137,
4202,
4254,
4282,
4311,
4326,
4328,
4361,
4393,
4422,
4424,
4426,
4473,
4502,
4562,
4564,
4566,
4603,
4664,
4711,
4820,
4841,
4864,
4878,
4931,
4948,
4973,
5014,
5016,
5058,
5092,
5094,
5096,
5136,
5138,
5160,
5211,
5218,
5220,
5240,
5273,
5310,
5332,
5448,
5523,
5539,
5551,
5584,
5620,
5642,
5758,
5930,
5981,
6123,
6253,
6436,
6452,
6475,
6515,
6531,
6543,
6576,
6617,
6639,
6755,
6889,
7003,
7129,
7145,
7168,
7209,
7225,
7237,
7267,
7309,
7338,
7516,
7528,
7558,
7600,
7631,
7737,
7749,
7779,
7822,
7850,
8024,
8036,
8077,
8118,
8201,
8213,
8220,
8275,
8305,
8331,
8357,
8409,
8411,
8441,
8486,
8500,
8515,
8517,
8559,
8561,
8627,
8629,
8631,
8663,
8673,
8675,
8690,
8713,
8756,
8758,
8827,
8868,
8870,
8892,
8964,
9036,
9070,
9083,
9163,
9213,
9277,
9279,
9281,
9311,
9337,
9339,
9361,
9363,
9415,
9461,
9487,
9533,
9535,
9573,
9631,
9691,
9693,
9750,
9813,
9815,
9858,
9860,
9895,
9897,
9931,
9972,
9998,
10044,
10091,
10093,
10108,
10131,
10174,
10176,
10245,
10286,
10288,
10310,
10382,
10454,
10488,
10501,
10581,
10631,
10695,
10697,
10712,
10737,
10790,
10834,
10880,
10904,
10930,
10932,
10970,
11028,
11088,
11090,
11147,
11210,
11212,
11255,
11257,
11292,
11294,
11311,
11352,
11354,
11417,
11470,
11472,
11474,
11507,
11544,
11591,
11593,
11608,
11659,
11730,
11791,
11867,
11938,
12014,
12016,
12032,
12100,
12177,
12248,
12283,
12326,
12372,
12450,
12524,
12601,
12673,
12675,
12690,
12719,
12756,
12758,
12773,
12798,
12846,
12848,
12888,
12943,
12945,
13011,
13047,
13060,
13095,
13097,
13161,
13212,
13214,
13235,
13237,
13278,
13329,
13383,
13445,
13514,
13534,
13536,
13600,
13666,
13732,
13734,
13758,
13834,
13836,
13853,
13883,
13885,
13887,
13920,
13962,
14000,
14002,
14075,
14120,
14129,
14167,
14217,
14265,
14344,
14346,
14370,
14402,
14404,
14421,
14496,
14527,
14529,
14531,
14564,
14602,
14641,
14643,
14707,
14780,
14845,
14884,
14893,
14968,
15032,
15091,
15093,
15117,
15144,
15146,
15148,
15177,
15214,
15256,
15260,
15266,
15267,
15268,
15269,
15318
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 15318,
"ccnet_original_nlines": 418,
"rps_doc_curly_bracket": 0.0002611299860291183,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.13527850806713104,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.006299729924649,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.4990053176879883,
"rps_doc_frac_unique_words": 0.3907225728034973,
"rps_doc_mean_word_length": 8.457627296447754,
"rps_doc_num_sentences": 230,
"rps_doc_symbol_to_word_ratio": 0.004310340154916048,
"rps_doc_unigram_entropy": 5.5561299324035645,
"rps_doc_word_count": 1121,
"rps_doc_frac_chars_dupe_10grams": 0.15209366381168365,
"rps_doc_frac_chars_dupe_5grams": 0.2382660061120987,
"rps_doc_frac_chars_dupe_6grams": 0.23151566088199615,
"rps_doc_frac_chars_dupe_7grams": 0.19090813398361206,
"rps_doc_frac_chars_dupe_8grams": 0.1782512366771698,
"rps_doc_frac_chars_dupe_9grams": 0.16137537360191345,
"rps_doc_frac_chars_top_2gram": 0.030060119926929474,
"rps_doc_frac_chars_top_3gram": 0.03955278918147087,
"rps_doc_frac_chars_top_4gram": 0.006750340107828379,
"rps_doc_books_importance": -1530.893310546875,
"rps_doc_books_importance_length_correction": -1530.893310546875,
"rps_doc_openwebtext_importance": -704.6773071289062,
"rps_doc_openwebtext_importance_length_correction": -704.6773071289062,
"rps_doc_wikipedia_importance": -766.8610229492188,
"rps_doc_wikipedia_importance_length_correction": -766.8610229492188
},
"fasttext": {
"dclm": 0.999477207660675,
"english": 0.5481722354888916,
"fineweb_edu_approx": 1.1245123147964478,
"eai_general_math": 0.6605890989303589,
"eai_open_web_math": 0.5321137309074402,
"eai_web_code": 0.13027024269104004
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.02",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "4",
"label": "Analyze"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "4",
"label": "Code/Software"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "3",
"label": "Academic Writing"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "4",
"label": "Graduate/Expert Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
5,626,112,212,512,189,000
|
Create
cancel
Showing results for
Search instead for
Did you mean:
Sign up Log in
Celebration
Earn badges and make progress
You're on your way to the next level! Join the Kudos program to earn points and save your progress.
Deleted user Avatar
Deleted user
Level 1: Seed
25 / 150 points
Next: Root
Avatar
1 badge earned
Collect
Participate in fun challenges
Challenges come and go, but your rewards stay with you. Do more to earn more!
Challenges
Coins
Gift kudos to your peers
What goes around comes around! Share the love by gifting kudos to your peers.
Recognition
Ribbon
Rise up in the ranks
Keep earning points to reach the top of the leaderboard. It resets every quarter so you always have a chance!
Leaderboard
Customised hierarchy
This question is in reference to Atlassian Documentation: Configuring initiatives and other hierarchy levels
I'd like to create the following hierarchy levels:
1. Initiative (a big strategic topic, covers typically several projets)
1. Epic (typically a big project)
1. Story (a part of that project, mostly a specific stage of the projet)
1. Task (Task within a story or project stage)
1. Sub-Task (Classical sub-task of a bigger task)
However, I don't know how to change the default hierarchy:
1. Epic
1. Story
1. Sub-Task
I can create an Initiative above Epic, but I cannot introduce a Task between Story and Sub-Task.
How can I adapt the default hierarchy to the 5 levels specified above? Is it possible at all? If nont what would you suggest to get those 5 levels?
Stef
1 answer
1 accepted
0 votes
Answer accepted
Nic Brough -Adaptavist-
Community Leader
Community Leader
Community Leaders are connectors, ambassadors, and mentors. On the online community, they serve as thought leaders, product experts, and moderators.
Dec 19, 2016
JIRA does not have a changeable hierarchy.
JIRA Core allows for Project, Issue/Story, Sub-task. (You could argue that Category groups projects and you can use components to break down issues within a project into other groups, but I don't see those as hierarchical)
JIRA Software adds Epics to that, converting the issue type to behave as a container for stories and issues.
JIRA Portfolio adds Initiatives.
And that's it really. You can't wedge other layers in, it's simply not supported, as the hierarchy is hard coded.
If you're on Server versions, you could add the Structure add-on, as that plays some tricks that makes it look like there are more layers within the Project/Story/Subtask framework, and it does it reliably and clearly.
Thanks Nic, short and clear.
Suggest an answer
Log in or Sign up to answer
TAGS
AUG Leaders
Atlassian Community Events
|
{
"url": "https://community.atlassian.com/t5/Advanced-planning-questions/Customised-hierarchy/qaq-p/398093",
"source_domain": "community.atlassian.com",
"snapshot_id": "CC-MAIN-2023-50",
"warc_metadata": {
"Content-Length": "185566",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:6ER4KUYAY4AQLFCQTBQ5HJECX6UXVCON",
"WARC-Concurrent-To": "<urn:uuid:fd177717-fc49-4953-9fd1-6ecd09fd68f3>",
"WARC-Date": "2023-12-04T06:56:05Z",
"WARC-IP-Address": "52.85.151.5",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:EG4NADFD62WADMD7LT56ZSYOI4E4L4P5",
"WARC-Record-ID": "<urn:uuid:704b324a-bcac-4c68-983e-0476637dc74d>",
"WARC-Target-URI": "https://community.atlassian.com/t5/Advanced-planning-questions/Customised-hierarchy/qaq-p/398093",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:6bb30564-3ff9-4e33-aad9-5fdf5ecc7c3f>"
},
"warc_info": "isPartOf: CC-MAIN-2023-50\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for November/December 2023\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-94\r\nsoftware: Apache Nutch 1.19 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.5-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
7,
14,
35,
55,
70,
85,
97,
98,
128,
129,
229,
230,
250,
263,
264,
278,
279,
295,
296,
307,
308,
315,
316,
331,
332,
340,
341,
371,
372,
450,
451,
462,
468,
469,
494,
495,
573,
574,
586,
593,
594,
615,
616,
726,
727,
739,
740,
761,
762,
871,
872,
923,
924,
998,
1036,
1115,
1170,
1230,
1231,
1291,
1292,
1302,
1315,
1333,
1334,
1431,
1432,
1580,
1581,
1586,
1587,
1596,
1597,
1608,
1609,
1617,
1633,
1657,
1674,
1691,
1840,
1853,
1854,
1898,
1899,
2123,
2124,
2233,
2234,
2267,
2268,
2384,
2385,
2604,
2605,
2635,
2636,
2654,
2655,
2683,
2688,
2700,
2701
],
"line_end_idx": [
7,
14,
35,
55,
70,
85,
97,
98,
128,
129,
229,
230,
250,
263,
264,
278,
279,
295,
296,
307,
308,
315,
316,
331,
332,
340,
341,
371,
372,
450,
451,
462,
468,
469,
494,
495,
573,
574,
586,
593,
594,
615,
616,
726,
727,
739,
740,
761,
762,
871,
872,
923,
924,
998,
1036,
1115,
1170,
1230,
1231,
1291,
1292,
1302,
1315,
1333,
1334,
1431,
1432,
1580,
1581,
1586,
1587,
1596,
1597,
1608,
1609,
1617,
1633,
1657,
1674,
1691,
1840,
1853,
1854,
1898,
1899,
2123,
2124,
2233,
2234,
2267,
2268,
2384,
2385,
2604,
2605,
2635,
2636,
2654,
2655,
2683,
2688,
2700,
2701,
2727
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 2727,
"ccnet_original_nlines": 103,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3473491668701172,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.021937839686870575,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.19744059443473816,
"rps_doc_frac_unique_words": 0.5328798294067383,
"rps_doc_mean_word_length": 4.775510311126709,
"rps_doc_num_sentences": 31,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 5.116054534912109,
"rps_doc_word_count": 441,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.005698009859770536,
"rps_doc_frac_chars_top_3gram": 0.010446339845657349,
"rps_doc_frac_chars_top_4gram": 0.015194679610431194,
"rps_doc_books_importance": -218.728759765625,
"rps_doc_books_importance_length_correction": -218.728759765625,
"rps_doc_openwebtext_importance": -143.9518585205078,
"rps_doc_openwebtext_importance_length_correction": -143.9518585205078,
"rps_doc_wikipedia_importance": -116.63621520996094,
"rps_doc_wikipedia_importance_length_correction": -116.63621520996094
},
"fasttext": {
"dclm": 0.849659264087677,
"english": 0.9138052463531494,
"fineweb_edu_approx": 1.542382836341858,
"eai_general_math": 0.013893069699406624,
"eai_open_web_math": 0.12299281358718872,
"eai_web_code": 0.0025517900940030813
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.452",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "658.403",
"labels": {
"level_1": "Industrial arts, Technology, and Engineering",
"level_2": "Business",
"level_3": "Management"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "6",
"label": "Indeterminate"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "1",
"label": "General Audience"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
4,471,140,104,141,718,500
|
Rumored Buzz on programming homework help
Abstraction is crucial in the construction of plans. It locations the emphasis on what an item is or does as opposed to the way it is represented or how it works. Therefore, it truly is the key implies of controlling complexity in significant programs.
In that feeling, encapsulation also allows a class to vary its internal implementation without the need of hurting the overall performing in the technique. That idea of encapsulation is to cover how a category does its small business, although allowing for other lessons to make requests of it.
I found your short article usually precise and beneficial, Regardless of several spelling and grammatical problems. On the other hand, I have to say that the posting's protection of OOP is extremely sophisticated. This is not your fault nevertheless the fault of OOP as portrayed by languages like C#, Java, and C++.
"In genuine entire world, you can generally discover a lot of specific objects all of the exact sort. As an example, there might be A huge number of other bicycles in existence, each of the very same make and product.
This will not be a feasible solution, and it only limitations the impact into the working method; the remainder of your software should be matter to compromise. Be mindful to prevent CWE-243 and other weaknesses connected to jails. Performance: Confined Notes: The usefulness of this mitigation is determined by the avoidance abilities of the particular sandbox or jail being used and may only help to decrease the scope of an attack, such as restricting the attacker to certain system calls or restricting the percentage of the file system which can be accessed.
applying Process; community course Sophisticated non-public int actual; community int True get return real; personal int imaginary; community int Imaginary get return imaginary; public Complex(int genuine, int imaginary) this.
Therefore the conclusion might be the two design and style patterns exist to take look at this site care of two sort of business enterprise problems, so Though They give the impression of being related, they're not.
Abstraction is a knockout post an emphasis on the idea, qualities and Houses instead of the particulars (a suppression of element). The value of abstraction is derived from its power to disguise irrelevant facts and from the usage of names to reference objects.
"As numerous many years pass by, these developers turn into leads and software program architects. Their titles transform, but the aged legacy of not comprehension, of not obtaining any architectural knowledge, continues, developing a vacuum of excellent architects.
The obtain modifier of the constructor on the LoggerBase is guarded. Find Out More The public constructor has no use when The category is of style summary. The summary classes usually are not allowed to instantiate The category. So I went for your secured constructor.
In summary the Interface separates the implementation and defines the structure, and this idea is very practical in circumstances where you need to have the implementation to become interchangeable.
Nonetheless a very well-described course should be a meaningful grouping of the set of capabilities and will guidance the reusability, while rising expandability or maintainability, of the general system.
public course Elaborate non-public int serious; public int you can try this out Real get return serious; non-public int imaginary; community int Imaginary get return imaginary; general public Elaborate(int true, int imaginary) this.
Learn about the excellence concerning declaring a variable, class or operate--and defining it--and why it issues when you have issues compiling your code
Leave a Reply
Your email address will not be published. Required fields are marked *
|
{
"url": "http://programming-project-help08416.getblogs.net/6416413/rumored-buzz-on-programming-homework-help",
"source_domain": "programming-project-help08416.getblogs.net",
"snapshot_id": "crawl=CC-MAIN-2018-26",
"warc_metadata": {
"Content-Length": "14409",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:LXTLB6DGZS4DBYFGNEQJHUCAP57JGQDU",
"WARC-Concurrent-To": "<urn:uuid:bf528693-eb30-4252-8ac5-d47750cef465>",
"WARC-Date": "2018-06-20T10:51:06Z",
"WARC-IP-Address": "66.35.68.186",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:B7Y6QJXVKTY76ENYYGMOSUWYMTPLMEVV",
"WARC-Record-ID": "<urn:uuid:5ed23640-ac2a-4c7c-b68d-f50e0f20fa4e>",
"WARC-Target-URI": "http://programming-project-help08416.getblogs.net/6416413/rumored-buzz-on-programming-homework-help",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:d3f3e957-6cf0-4823-a307-7761bad1c661>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-144-111-253.ec2.internal\r\nsoftware: Nutch 1.6 (CC)\r\nisPartOf: CC-MAIN-2018-26\r\noperator: Common Crawl Admin\r\ndescription: Wide crawl of the web for June 2018\r\npublisher: Common Crawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
42,
43,
44,
45,
298,
299,
594,
595,
912,
913,
1131,
1132,
1696,
1697,
1924,
1925,
2141,
2142,
2404,
2405,
2672,
2673,
2942,
2943,
3142,
3143,
3348,
3349,
3582,
3583,
3737,
3738,
3752,
3753
],
"line_end_idx": [
42,
43,
44,
45,
298,
299,
594,
595,
912,
913,
1131,
1132,
1696,
1697,
1924,
1925,
2141,
2142,
2404,
2405,
2672,
2673,
2942,
2943,
3142,
3143,
3348,
3349,
3582,
3583,
3737,
3738,
3752,
3753,
3823
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 3823,
"ccnet_original_nlines": 34,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.431654691696167,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.012949639931321144,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.11942446231842041,
"rps_doc_frac_unique_words": 0.5199335217475891,
"rps_doc_mean_word_length": 5.1744184494018555,
"rps_doc_num_sentences": 28,
"rps_doc_symbol_to_word_ratio": 0.0014388499548658729,
"rps_doc_unigram_entropy": 5.181187152862549,
"rps_doc_word_count": 602,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.03274478018283844,
"rps_doc_frac_chars_dupe_6grams": 0.03274478018283844,
"rps_doc_frac_chars_dupe_7grams": 0.03274478018283844,
"rps_doc_frac_chars_dupe_8grams": 0.03274478018283844,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.012841089628636837,
"rps_doc_frac_chars_top_3gram": 0.005778490100055933,
"rps_doc_frac_chars_top_4gram": 0.015409310348331928,
"rps_doc_books_importance": -341.3392639160156,
"rps_doc_books_importance_length_correction": -341.3392639160156,
"rps_doc_openwebtext_importance": -186.03433227539062,
"rps_doc_openwebtext_importance_length_correction": -186.03433227539062,
"rps_doc_wikipedia_importance": -177.30752563476562,
"rps_doc_wikipedia_importance_length_correction": -177.30752563476562
},
"fasttext": {
"dclm": 0.20779085159301758,
"english": 0.9237700700759888,
"fineweb_edu_approx": 2.2698686122894287,
"eai_general_math": 0.061084091663360596,
"eai_open_web_math": 0.12408649921417236,
"eai_web_code": 0.02777748927474022
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.0151",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "10",
"label": "Knowledge Article"
},
"secondary": {
"code": "23",
"label": "Tutorial"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
3,562,765,765,672,462,300
|
Linux df command
Updated: 05/04/2019 by Computer Hope
df command
On Unix-like operating systems, the df command reports the amount of available disk space used by file systems.
This page covers the GNU/Linux version of df.
Description
df displays the amount of disk space available on the file system containing each file name argument. If no file name is given, the space available on all currently mounted file systems is shown. Disk space is shown in 1 K blocks by default, unless the environment variable POSIXLY_CORRECT is set, in which case 512-byte blocks are used.
If an argument is the absolute file name of a disk device node containing a mounted file system, df shows the space available on that file system rather than on the file system containing the device node (which is always the root file system). df cannot show the space available on unmounted file systems, because on most kinds of systems doing so requires very system-specific knowledge of file system structures.
Syntax
df [OPTION]... [FILE]...
Options
-a, --all Include dummy file systems.
-B,
--block-size=SIZE
Scale sizes by SIZE before printing them (e.g., '-BM' prints sizes in units of 1,048,576 bytes). See "SIZE Format" below for more information.
--total Display a grand total.
-h,
--human-readable
Print sizes in human readable format (e.g., 1K 234M 2G).
-H, --si Same as -h, but use powers of 1000 instead of 1024.
-i, --inodes List inode information instead of block usage.
-k Like --block-size=1K.
-l, --local Limit listing to local file systems.
--no-sync Do not invoke a sync before getting usage info, which is the default setting.
-P, --portability Use the POSIX output format.
--sync Invoke a sync before getting usage info.
-t, --type=TYPE Limit listing to file systems of type TYPE.
-T, --print-type Print file system type.
-x,
--exclude-type=TYPE
Limit listing to file systems not of type TYPE.
-v Ignored; included for compatibility reasons.
--help Display a help message and exit.
--version Output version information and exit.
SIZE Format
Display values are in units of the first available SIZE from --block-size, and the DF_BLOCK_SIZE, BLOCK_SIZE and BLOCKSIZE environment variables. Otherwise, units default to 1024 bytes (or 512 if POSIXLY_CORRECT is set).
SIZE is an integer and optional unit (example: 10M is 10*1024*1024). Units are K, M, G, T, P, E, Z, Y (powers of 1024) or KB, MB, ... (powers of 1000).
Examples
df
Display all file systems and their disk usage, as in the following output:
Filesystem 1K-blocks Used Available Use% Mounted on
/dev/loop0 18761008 15246876 2554440 86% /
none 4 0 4 0% /sys/fs/cgroup
udev 493812 4 493808 1% /dev
tmpfs 100672 1364 99308 2% /run
none 5120 0 5120 0% /run/lock
none 503352 1764 501588 1% /run/shm
none 102400 20 102380 1% /run/user
/dev/sda3 174766076 164417964 10348112 95% /host
df -h
Same as above, but use "human readable" formatting, as in the following example:
Filesystem Size Used Avail Use% Mounted on
/dev/loop0 18G 15G 2.5G 86% /
none 4.0K 0 4.0K 0% /sys/fs/cgroup
udev 483M 4.0K 483M 1% /dev
tmpfs 99M 1.4M 97M 2% /run
none 5.0M 0 5.0M 0% /run/lock
none 492M 1.8M 490M 1% /run/shm
none 100M 20K 100M 1% /run/user
/dev/sda3 167G 157G 9.9G 95% /host
df public_html
Display the amount of free space in the public_html directory, as in the following output:
Filesystem 1K-blocks Used Available Use% Mounted on
/dev/loop0 18761008 15246924 2554392 86% /
du — Report the amount of disk space used by a file or files.
find — Find files within a directory hierarchy.
ls — List the contents of a directory or directories.
|
{
"url": "https://www.computerhope.com/unix/udf.htm",
"source_domain": "www.computerhope.com",
"snapshot_id": "crawl=CC-MAIN-2021-39",
"warc_metadata": {
"Content-Length": "16003",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:JFDYQC4WFG5Y3ETHX3OTQEFZWKO5LDD7",
"WARC-Concurrent-To": "<urn:uuid:82455b7d-6150-4fce-b9c2-eed852b7b37e>",
"WARC-Date": "2021-09-22T10:27:20Z",
"WARC-IP-Address": "104.20.18.53",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:DHCIZ457TZBIJH3AL5DR2KAEGRF6J2HE",
"WARC-Record-ID": "<urn:uuid:b9d3fb7c-d3dc-4b94-966c-5dc6336e1746>",
"WARC-Target-URI": "https://www.computerhope.com/unix/udf.htm",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:a7ee2af1-46f5-4cc3-abb1-9d905bc5b1c7>"
},
"warc_info": "isPartOf: CC-MAIN-2021-39\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for September 2021\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-43\r\nsoftware: Apache Nutch 1.18 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.2-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
17,
18,
55,
66,
67,
179,
180,
226,
227,
239,
240,
578,
579,
994,
995,
1002,
1003,
1028,
1029,
1037,
1038,
1076,
1080,
1098,
1241,
1272,
1276,
1293,
1350,
1411,
1471,
1496,
1545,
1633,
1680,
1728,
1788,
1829,
1833,
1853,
1901,
1949,
1989,
2036,
2037,
2049,
2050,
2271,
2272,
2424,
2425,
2434,
2435,
2438,
2439,
2514,
2515,
2576,
2628,
2693,
2748,
2803,
2863,
2922,
2982,
3038,
3044,
3045,
3126,
3127,
3176,
3216,
3269,
3312,
3355,
3403,
3450,
3498,
3542,
3557,
3558,
3649,
3650,
3710,
3761,
3762,
3824,
3872
],
"line_end_idx": [
17,
18,
55,
66,
67,
179,
180,
226,
227,
239,
240,
578,
579,
994,
995,
1002,
1003,
1028,
1029,
1037,
1038,
1076,
1080,
1098,
1241,
1272,
1276,
1293,
1350,
1411,
1471,
1496,
1545,
1633,
1680,
1728,
1788,
1829,
1833,
1853,
1901,
1949,
1989,
2036,
2037,
2049,
2050,
2271,
2272,
2424,
2425,
2434,
2435,
2438,
2439,
2514,
2515,
2576,
2628,
2693,
2748,
2803,
2863,
2922,
2982,
3038,
3044,
3045,
3126,
3127,
3176,
3216,
3269,
3312,
3355,
3403,
3450,
3498,
3542,
3557,
3558,
3649,
3650,
3710,
3761,
3762,
3824,
3872,
3925
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 3925,
"ccnet_original_nlines": 88,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.233021080493927,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.07494144886732101,
"rps_doc_frac_lines_end_with_ellipsis": 0.011235959827899933,
"rps_doc_frac_no_alph_words": 0.33957844972610474,
"rps_doc_frac_unique_words": 0.4423728883266449,
"rps_doc_mean_word_length": 4.622034072875977,
"rps_doc_num_sentences": 48,
"rps_doc_symbol_to_word_ratio": 0.003512880066409707,
"rps_doc_unigram_entropy": 5.157089710235596,
"rps_doc_word_count": 590,
"rps_doc_frac_chars_dupe_10grams": 0.059405941516160965,
"rps_doc_frac_chars_dupe_5grams": 0.1349468231201172,
"rps_doc_frac_chars_dupe_6grams": 0.08360835909843445,
"rps_doc_frac_chars_dupe_7grams": 0.08360835909843445,
"rps_doc_frac_chars_dupe_8grams": 0.059405941516160965,
"rps_doc_frac_chars_dupe_9grams": 0.059405941516160965,
"rps_doc_frac_chars_top_2gram": 0.03226989135146141,
"rps_doc_frac_chars_top_3gram": 0.016134949401021004,
"rps_doc_frac_chars_top_4gram": 0.020902089774608612,
"rps_doc_books_importance": -358.3074035644531,
"rps_doc_books_importance_length_correction": -358.3074035644531,
"rps_doc_openwebtext_importance": -181.7368621826172,
"rps_doc_openwebtext_importance_length_correction": -181.7368621826172,
"rps_doc_wikipedia_importance": -153.51930236816406,
"rps_doc_wikipedia_importance_length_correction": -153.51930236816406
},
"fasttext": {
"dclm": 0.09232324361801147,
"english": 0.7194707989692688,
"fineweb_edu_approx": 2.6413943767547607,
"eai_general_math": 0.8480738401412964,
"eai_open_web_math": 0.2752525806427002,
"eai_web_code": 0.9929680824279785
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.445",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.67",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "10",
"label": "Knowledge Article"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-308,457,638,894,763,100
|
Beefy Boxes and Bandwidth Generously Provided by pair Networks
Syntactic Confectionery Delight
PerlMonks
The accidental fractal
by jimt (Chaplain)
on Sep 23, 2006 at 13:43 UTC ( #574513=obfuscated: print w/ replies, xml ) Need Help??
So I was golfing down my code for my Game of Life and had gotten down to 287 characters. But I could use one of the tricks I thought up to shave down teamster_jr's version to 285 characters, so I wasn't going to claim the lead yet.
I flipped around the logic in the main conditional and shaved it down to 283 characters (I thought) and figured that would do it. But instead of playing the game of life, the gameboard instantly converged on the sierpinski gasket. That's right - instead of creating a shorter version of the game of life, I'd accidentally created a fractal generator.
I went through and ripped out all the unnecessary game of life stuff from it (looping, timers, random seeding of cells, etc.) and the result is a pure ascii output of the sierpinski gasket. I also re-formatted it to be somewhat easier to read, but remember, this is the result of golfing and obfuscation, so it still won't be that easy to read.
my $s = 150; @a = 0..$s; for $r (@a) { $b[$r][$_] = $" for @a } { for $r (@a) { for (@a) { $h = 0; for $i ($r-1..$r+1) { for $j ($_-1..$_+1) { $h++ if $b[$i][$j] ne $" & $i >= 0 & $i <= $s & $j >= 0 & $j <= $s & $i ^ $r & $j ^ $_ } } $e[$r][$_] = $h == 3 ? 0 : $b[$r][$_] ne $" & $h == 2 ? 0 : $" } } print map{ @{$e[$_]}, $/ } @a; }
I just think it's incredible that an incorrect application of DeMorgan's rules was all it took to turn the game of life into the sierpinski gasket. Stephen Wolfram would be proud of me. It sure made my day.
Comment on The accidental fractal
Download Code
Re: The accidental fractal
by jwkrahn (Monsignor) on Sep 23, 2006 at 21:14 UTC
You can shorten this:
for $r (@a) { $b[$r][$_] = $" for @a }
To this:
@b = ([($")x@a])x@a;
You can also shorten this:
print map{ @{$e[$_]}, $/ } @a;
using the for statment modifier:
print @{$e[$_]}, $/ for @a;
Log In?
Username:
Password:
What's my password?
Create A New User
Node Status?
node history
Node Type: obfuscated [id://574513]
Approved by davidrw
help
Chatterbox?
and the web crawler heard nothing...
How do I use this? | Other CB clients
Other Users?
Others making s'mores by the fire in the courtyard of the Monastery: (14)
As of 2015-07-03 13:01 GMT
Sections?
Information?
Find Nodes?
Leftovers?
Voting Booth?
The top three priorities of my open tasks are (in descending order of likelihood to be worked on) ...
Results (53 votes), past polls
|
{
"url": "http://www.perlmonks.org/?node_id=574513",
"source_domain": "www.perlmonks.org",
"snapshot_id": "crawl=CC-MAIN-2015-27",
"warc_metadata": {
"Content-Length": "22530",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:ADXZYO7LUN4TSPEUMMO4BALWAMFOHAXT",
"WARC-Concurrent-To": "<urn:uuid:405cb8dc-1b72-45da-bac2-4bd46d5e1b53>",
"WARC-Date": "2015-07-03T13:04:11Z",
"WARC-IP-Address": "66.39.54.27",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:T7YNAV4VHCM6SQLOMXKPD6LQNIWGRNHQ",
"WARC-Record-ID": "<urn:uuid:afc08fe7-b5c5-4a3b-9e65-e26d6da296cc>",
"WARC-Target-URI": "http://www.perlmonks.org/?node_id=574513",
"WARC-Truncated": "length",
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:fe525050-e15f-4726-aa2f-e3035de07a5d>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-179-60-89.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2015-27\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web for June 2015\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
63,
95,
97,
109,
110,
133,
134,
153,
240,
241,
473,
474,
825,
826,
1171,
1172,
1506,
1507,
1714,
1715,
1749,
1763,
1790,
1842,
1868,
1911,
1924,
1949,
1980,
2015,
2052,
2084,
2085,
2093,
2103,
2113,
2114,
2134,
2152,
2165,
2178,
2214,
2234,
2239,
2251,
2288,
2289,
2327,
2340,
2414,
2441,
2451,
2464,
2476,
2487,
2505,
2506,
2612,
2613,
2614,
2615,
2616,
2617,
2618,
2619,
2620,
2621
],
"line_end_idx": [
63,
95,
97,
109,
110,
133,
134,
153,
240,
241,
473,
474,
825,
826,
1171,
1172,
1506,
1507,
1714,
1715,
1749,
1763,
1790,
1842,
1868,
1911,
1924,
1949,
1980,
2015,
2052,
2084,
2085,
2093,
2103,
2113,
2114,
2134,
2152,
2165,
2178,
2214,
2234,
2239,
2251,
2288,
2289,
2327,
2340,
2414,
2441,
2451,
2464,
2476,
2487,
2505,
2506,
2612,
2613,
2614,
2615,
2616,
2617,
2618,
2619,
2620,
2621,
2655
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 2655,
"ccnet_original_nlines": 67,
"rps_doc_curly_bracket": 0.009039550088346004,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.32234957814216614,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.022922640666365623,
"rps_doc_frac_lines_end_with_ellipsis": 0.029411759227514267,
"rps_doc_frac_no_alph_words": 0.38252148032188416,
"rps_doc_frac_unique_words": 0.5381062626838684,
"rps_doc_mean_word_length": 4.136258602142334,
"rps_doc_num_sentences": 31,
"rps_doc_symbol_to_word_ratio": 0.004297989886254072,
"rps_doc_unigram_entropy": 5.01270866394043,
"rps_doc_word_count": 433,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.026800669729709625,
"rps_doc_frac_chars_dupe_6grams": 0.01228363998234272,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.01675041951239109,
"rps_doc_frac_chars_top_3gram": 0.02791736088693142,
"rps_doc_frac_chars_top_4gram": 0.021775539964437485,
"rps_doc_books_importance": -266.5931091308594,
"rps_doc_books_importance_length_correction": -266.5931091308594,
"rps_doc_openwebtext_importance": -169.16944885253906,
"rps_doc_openwebtext_importance_length_correction": -169.16944885253906,
"rps_doc_wikipedia_importance": -184.32443237304688,
"rps_doc_wikipedia_importance_length_correction": -184.32443237304688
},
"fasttext": {
"dclm": 0.12226206064224243,
"english": 0.8887366056442261,
"fineweb_edu_approx": 1.305065631866455,
"eai_general_math": 0.06966304779052734,
"eai_open_web_math": 0.18118596076965332,
"eai_web_code": 0.0010861200280487537
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "514.742",
"labels": {
"level_1": "Science and Natural history",
"level_2": "Mathematics",
"level_3": "Trigonometry and Topology"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "4",
"label": "Analyze"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "4",
"label": "Code/Software"
},
"secondary": {
"code": "5",
"label": "Social/Forum"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "16",
"label": "Personal Blog"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-4,027,581,537,900,875,300
|
how to fix err connection timed out
How To Fix Err Connection Timed Out?
How to Fix the ERR_CONNECTION_TIMED_OUT Error
1. Check Your Connection. Google Chrome, Firefox, and Edge all recommend that you should check your network connection. …
2. Disable Firewall and Antivirus Software Temporarily. …
3. Disable Proxy Settings. …
4. Change DNS Servers.
How do I fix err timeout on Chrome?
1. Tap More Settings.
2. Under “Advanced,” tap Privacy Clear browsing data.
3. Next to “Time range,” choose All time.
4. Select Cookies and site data and Cached images and files. Deselect the other types of data.
5. Tap Clear data.
6. Try reloading the tab with the error.
Why do you get connection timed out or connection failed errors?
“Connection timed out” is an error that occurs as a result of a script exceeding the maximum timeout value. If a client connection does not receive a response from the server after approximately 30 to 60 seconds the load balancer will close the connection and the client will immediately receive the error message.
What does it mean when connection is timed out?
A server connection timeout means that a server is taking too long to reply to a data request made from another device. … Timeout errors can happen for a number of reasons. The server, the requesting device, the network hardware and even an Internet connection can be at fault.
Why does Google Chrome timeout so often?
Often, the reason your connection might be getting timed out is due to cookies or caches becoming corrupted and creating problems in establishing a connection between your browser and the website’s server. Therefore, a good option is to clear your browsing data from your Google Chrome.
How do I increase timeout in Chrome?
2 Answers. Chrome: It is not possible to change the timeout settings in Chrome. IE: It’s possible to change the timeout behavior in the windows registry. Safari: There is a safari extension SafariNoTimeout to extend the timeout from 60s to 10min.
How do I fix my connection timeout on my iPhone?
How to Fix iTunes Network and iPhone Update Connection Errors
1. Disable Firewall and Anti-Virus. This is often the simplest solution and this is what you should try first. …
2. Uninstall and Re-install iTunes. …
3. Flush DNS Cache. …
4. Manually Download the iOS Update. …
5. iTunes Error 9808.
How do I change my default timeout?
System timeouts are set within the Settings application.
1. Select the Settings button on the Home screen.
2. The Settings screen displays. …
3. Select Timeouts.
4. Select the appropriate timeout from the list and then select the Open timeout button.
5. Select and drag the control button along the slide bar to adjust the timeout.
READ: how do pizza stones work
How do I increase my connection timeout?
Set the keep-alive options in the client configuration file:
Login to the client machine and open the /etc/ssh/ssh_config file to set the necessary parameter values to increase the SS connection timeout. ServerAliveInterval and ServerAliveCountMax parameters are set to increase the connection timeout.
What is err connection?
If you want to access a website with your browser and you receive the message “ERR_CONNECTION_RESET” instead, it means that the connection could not be established correctly. As a result, the connection has been “reset.” ERR_CONNECTION_RESET error message. This site can’t be reached. The connection was reset.
What is timeout error?
Methods to Fix a 408 Request Timeout Error
The 408 Request Timeout error is an HTTP status code that means the request you sent to the website server—e.g., a request to load a web page—took longer than the website’s server was prepared to wait. In other words, your connection with the website “timed out.”
How do you fix timeout error in Minecraft?
How to fix Connection timed out error on Minecraft
1. Check Minecraft server status.
2. Reboot your network.
3. Allow Minecraft on your firewall.
4. Forward the 25565 Port in Windows Defender Firewall.
5. Temporarily Disable Your Antivirus program.
6. Switch to a different version of Minecraft.
7. Use a VPN.
What does Err_address_unreachable mean?
Users experience the error message “ERR_ADDRESS_UNREACHABLE” when they are unable to access certain websites on their computer. It should be mentioned beforehand that this issue can be either at your side or at the server side.
Does Chrome have a request timeout?
General purpose answer : Where can I find the default timeout settings for all browsers? Unfortunately, AFAIK there is no setting available in Chrome to set the timeout.
Why is my iPhone timing out?
The reason your iPhone keeps dimming and turning off is because of a feature called “Auto-Lock,” which automatically puts the iPhone into a sleep/lock mode after a certain period of time. Two-thirds of the way through the set period, the screen dims to half brightness. To fix it, we need to turn “Auto-Lock” off.
how to fix err connection timed out
how to fix err connection timed out
Why is iTunes timed out?
ITunes timeouts are often caused by a generally low-performing network connection. However, the issue can also be caused by software problems, such as your firewall erroneously blocking iTunes from connecting.
Why is my iTunes timing out?
Both Android and iOS users encounter one difficulty or another with Apple’s native music streaming service. … Sometimes, simply closing and reopening the Apple Music app works the magic and eliminates the error. Renabling your device’s cellular data/Wi-Fi does the trick as the error is majorly connectivity-related.
READ: what do crickets eat in a house
How do I stop my WIFI from timing out?
Connection timed out wifi – Best answers.
What you can also try:
1. Try another browser ;
2. Disable your different browser extensions ;
3. Restart your router ;
4. Update your router firmware ;
5. Use Google DNS.
How do I turn off network timeout?
Table of Contents
1. Clear Browser Cache.
2. Restart Internet Router.
3. Check and Update Browser.
4. Run Compatibility Mode.
5. Disable Faulty Extensions.
6. Use Browser’s Default Settings.
7. Unblock Blacklisted Sites.
8. Adjust the Lan Settings.
How do I fix connection timeout on Android?
Turn airplane mode on and off
1. Open your Settings app and tap Network & internet or Connections. Airplane Mode. Depending on your device, these options may be different.
2. Turn Airplane mode on.
3. Wait for 10 seconds.
4. Turn Airplane mode off.
5. Check if the connection problems have been solved.
Is Commandtimeout in seconds or milliseconds?
Yes, SQLCommand timeout property is set in seconds and milliseconds. No there is no way to change it to milliseconds, as per the documentation on MSDN.
How do I check connection timeout?
To test a connection timeout at the socket level, freeze the nc process with a kill -STOP <pid> (or just CTRL-Z it without putting in background). The system will act as if the server was running, but wait for the server to accept the connection, resulting in a connection timeout (errno 110).
How do I get past connection reset?
How do I fix chrome connection reset? If your site says err_connection_reset or the connection was reset try the following: Clear browser cache. Flush DNS cache.
FAQS
1. Check your internet connection.
2. Check your VPN and run a test.
3. Check Firewall settings.
4. Temporarily disable the antivirus.
5. Check LAN settings.
What causes connection reset?
More commonly, it is caused by writing to a connection that the other end has already closed normally. In other words an application protocol error. It can also be caused by closing a socket when there is unread data in the socket receive buffer.
Why do I keep getting connection reset?
‘Connection reset’ usually means the connection was unexpectedly closed by the peer. The server appears to have dropped the connection on the unsuspecting HTTP client before sending back a response. This is most likely due to the high load.
How do you fix the connection timed out on Minecraft?
How to fix the “connection timed out error” in Minecraft
1. Check the Minecraft server status.
2. Reboot your modem or router.
3. Allow Minecraft on your firewall.
4. Allow port 25565 in Windows Defender Firewall.
5. Temporarily disable your Antivirus program.
6. Try a different version of Minecraft.
7. Use a VPN to bypass blocks.
READ: what impact does ozone depletion have on plant and animal life?
Can no longer connect to Minecraft server?
Try disabling any existing firewall program, or changing its configuration options. Restart your modem/router. You may also want to try logging out of your account and then logging back in, as this refreshes your profile’s authentication and connection with our servers.
How do I allow port 25565 through my firewall?
How do I reset my Google Chrome settings?
Reset Chrome settings to default
1. On your computer, open Chrome.
2. At the top right, click More Settings. Advanced. On Chromebook, Linux, and Mac: Click Reset settings Restore settings to their original defaults. Reset settings. On Windows: Click Reset and cleanup Reset settings to their original defaults. Reset settings.
How do I clear my DNS cache in Chrome?
For Chrome, open a new tab and enter chrome://net-internals/#dns in the address bar and press Enter . Click on Clear host cache button to clear the browser’s DNS cache. No prompts or confirmation messages will be shown, but this simple action should flush Chrome’s DNS cache for you.
How do I fix this Err_address_unreachable?
How to fix: ERR_ADDRESS_UNREACHABLE in Chrome?
1. Restart your router and device.
2. Clear browsing data.
3. Clear Chrome DNS cache.
4. Bottom Line: ERR_ADDRESS_UNREACHABLE Chrome.
How do you hack screentime?
How kids are hacking it. This hack seems to be pretty obvious. Kids are just going to Settings, then to General – Date and Time screen. Then they are simply turning off Automatic Update and manually changing the current system date and time into the desired time period where all games are unlocked.
How do I get rid of the clock on my iPhone lock screen?
Question: Q: Remove time and date from lock screen
YOU NEED TO SWIPE FINGER FROM RIGHT CORNER TO DOWN AND THEN UPWARDS RIGHT CORNER TO REMOVE TIME FROM LOCK SCREEN.
[SOLVED] NET ERR_CONNECTION_TIMED_OUT Error Code Problem
Err connection timed out problem, How to Fix in Google Chrome || 2020 (4 Solutions Given)
How to Fix Network error : connection timed out putty?
How to Fix ERR TIMED OUT on Google Chrome
Related Searches
err_connection_timed_out code
how to fix err timed out on android
failed to load resource: net::err_connection_timed_out
error connection timed out android
err_connection_timed_out windows 10
error connection timed out android chrome
error 118 connection timed out
err connection timed out chrome
See more articles in category: FAQs
|
{
"url": "https://publicaffairsworld.com/how-to-fix-err-connection-timed-out/",
"source_domain": "publicaffairsworld.com",
"snapshot_id": "crawl=CC-MAIN-2022-21",
"warc_metadata": {
"Content-Length": "71381",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:RSCBQCFTHQAWFRVY2XVIO3KMWJQAPY7Z",
"WARC-Concurrent-To": "<urn:uuid:f9736b34-899d-4c92-b718-db5742cd112e>",
"WARC-Date": "2022-05-26T12:07:38Z",
"WARC-IP-Address": "104.21.88.200",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:XW772ZHKVC6SGYFGCNU4TZTNTTFWPANQ",
"WARC-Record-ID": "<urn:uuid:2101d155-a135-4c86-9132-38daca487ffb>",
"WARC-Target-URI": "https://publicaffairsworld.com/how-to-fix-err-connection-timed-out/",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:b4bc7a26-c76b-4ee5-a108-90d33c358b09>"
},
"warc_info": "isPartOf: CC-MAIN-2022-21\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for May 2022\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-215\r\nsoftware: Apache Nutch 1.18 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.3-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
36,
37,
74,
75,
121,
245,
305,
336,
361,
362,
398,
399,
423,
479,
523,
620,
641,
684,
685,
750,
751,
1066,
1067,
1115,
1116,
1394,
1395,
1436,
1437,
1724,
1725,
1762,
1763,
2010,
2011,
2060,
2061,
2123,
2238,
2278,
2302,
2343,
2367,
2368,
2404,
2405,
2462,
2514,
2551,
2573,
2664,
2747,
2779,
2780,
2821,
2822,
2883,
2884,
3126,
3127,
3151,
3152,
3463,
3464,
3487,
3488,
3531,
3532,
3796,
3797,
3840,
3841,
3892,
3928,
3954,
3993,
4051,
4100,
4149,
4165,
4166,
4206,
4207,
4435,
4436,
4472,
4473,
4643,
4644,
4673,
4674,
4988,
4989,
5025,
5061,
5062,
5087,
5088,
5298,
5299,
5328,
5329,
5646,
5647,
5686,
5687,
5726,
5727,
5769,
5770,
5793,
5820,
5869,
5896,
5931,
5952,
5953,
5988,
5989,
6007,
6033,
6063,
6094,
6123,
6155,
6192,
6224,
6254,
6255,
6299,
6300,
6330,
6474,
6502,
6528,
6557,
6613,
6614,
6660,
6661,
6813,
6814,
6849,
6850,
7144,
7145,
7181,
7182,
7344,
7345,
7350,
7387,
7423,
7453,
7493,
7518,
7519,
7549,
7550,
7797,
7798,
7838,
7839,
8080,
8081,
8135,
8136,
8193,
8233,
8267,
8306,
8358,
8407,
8450,
8483,
8554,
8555,
8598,
8599,
8870,
8871,
8918,
8919,
8961,
8962,
8995,
9031,
9293,
9294,
9333,
9334,
9618,
9619,
9662,
9663,
9710,
9747,
9773,
9802,
9852,
9853,
9881,
9882,
10182,
10183,
10239,
10240,
10291,
10292,
10406,
10407,
10464,
10465,
10555,
10556,
10611,
10612,
10654,
10655,
10672,
10673,
10703,
10739,
10794,
10829,
10865,
10907,
10938,
10970,
10971
],
"line_end_idx": [
36,
37,
74,
75,
121,
245,
305,
336,
361,
362,
398,
399,
423,
479,
523,
620,
641,
684,
685,
750,
751,
1066,
1067,
1115,
1116,
1394,
1395,
1436,
1437,
1724,
1725,
1762,
1763,
2010,
2011,
2060,
2061,
2123,
2238,
2278,
2302,
2343,
2367,
2368,
2404,
2405,
2462,
2514,
2551,
2573,
2664,
2747,
2779,
2780,
2821,
2822,
2883,
2884,
3126,
3127,
3151,
3152,
3463,
3464,
3487,
3488,
3531,
3532,
3796,
3797,
3840,
3841,
3892,
3928,
3954,
3993,
4051,
4100,
4149,
4165,
4166,
4206,
4207,
4435,
4436,
4472,
4473,
4643,
4644,
4673,
4674,
4988,
4989,
5025,
5061,
5062,
5087,
5088,
5298,
5299,
5328,
5329,
5646,
5647,
5686,
5687,
5726,
5727,
5769,
5770,
5793,
5820,
5869,
5896,
5931,
5952,
5953,
5988,
5989,
6007,
6033,
6063,
6094,
6123,
6155,
6192,
6224,
6254,
6255,
6299,
6300,
6330,
6474,
6502,
6528,
6557,
6613,
6614,
6660,
6661,
6813,
6814,
6849,
6850,
7144,
7145,
7181,
7182,
7344,
7345,
7350,
7387,
7423,
7453,
7493,
7518,
7519,
7549,
7550,
7797,
7798,
7838,
7839,
8080,
8081,
8135,
8136,
8193,
8233,
8267,
8306,
8358,
8407,
8450,
8483,
8554,
8555,
8598,
8599,
8870,
8871,
8918,
8919,
8961,
8962,
8995,
9031,
9293,
9294,
9333,
9334,
9618,
9619,
9662,
9663,
9710,
9747,
9773,
9802,
9852,
9853,
9881,
9882,
10182,
10183,
10239,
10240,
10291,
10292,
10406,
10407,
10464,
10465,
10555,
10556,
10611,
10612,
10654,
10655,
10672,
10673,
10703,
10739,
10794,
10829,
10865,
10907,
10938,
10970,
10971,
11006
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 11006,
"ccnet_original_nlines": 230,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3037857711315155,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.036472760140895844,
"rps_doc_frac_lines_end_with_ellipsis": 0.03463203087449074,
"rps_doc_frac_no_alph_words": 0.2012927085161209,
"rps_doc_frac_unique_words": 0.29530200362205505,
"rps_doc_mean_word_length": 4.835011005401611,
"rps_doc_num_sentences": 229,
"rps_doc_symbol_to_word_ratio": 0.005078489892184734,
"rps_doc_unigram_entropy": 5.457502841949463,
"rps_doc_word_count": 1788,
"rps_doc_frac_chars_dupe_10grams": 0.029381150379776955,
"rps_doc_frac_chars_dupe_5grams": 0.08397918194532394,
"rps_doc_frac_chars_dupe_6grams": 0.06709080189466476,
"rps_doc_frac_chars_dupe_7grams": 0.05968768149614334,
"rps_doc_frac_chars_dupe_8grams": 0.037709660828113556,
"rps_doc_frac_chars_dupe_9grams": 0.037709660828113556,
"rps_doc_frac_chars_top_2gram": 0.018507810309529305,
"rps_doc_frac_chars_top_3gram": 0.01110467966645956,
"rps_doc_frac_chars_top_4gram": 0.007634469773620367,
"rps_doc_books_importance": -829.952392578125,
"rps_doc_books_importance_length_correction": -829.952392578125,
"rps_doc_openwebtext_importance": -443.0300598144531,
"rps_doc_openwebtext_importance_length_correction": -443.0300598144531,
"rps_doc_wikipedia_importance": -322.5405578613281,
"rps_doc_wikipedia_importance_length_correction": -322.5405578613281
},
"fasttext": {
"dclm": 0.8192146420478821,
"english": 0.8540617823600769,
"fineweb_edu_approx": 1.5149822235107422,
"eai_general_math": 0.020814180374145508,
"eai_open_web_math": 0.059355560690164566,
"eai_web_code": 0.030472759157419205
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.67",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "23",
"label": "Tutorial"
},
"secondary": {
"code": "21",
"label": "Customer Support"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "1",
"label": "General Audience"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-8,850,565,560,886,928,000
|
5
Writing a CLI tool, I'm facing a conundrum.
The tool is supposed to detect faces in images and blur them automatically. However, sometimes only one of those things should be done to allow marking additional faces manually with an external tool. So there are three behaviours I want to support:
1. Detect faces and blur them in one go
2. Only detect faces
3. Only blur faces
My idea of solving this were two mutually exclusive options, something like --only-detect and --only-blur.
However, a coworker suggested that it might make more sense to have --detect and --blur, so that using both options would lead to the same behaviour as using none, but I find this to be less intuitive.
My question now is: Are there any conventions I can follow to make this decision? I found the POSIX Utility Conventions, and they do mention mutually exclusive groups, but nothing that is helpful here.
8
• 2
--only-foo is not something I think I've ever encountered in a tool; there's a few that do --no-foo, and --no-blur --no-detect wouldn't be mutually exclusive, nor would ` ` be the same as --blur --detect. Commented Nov 14, 2017 at 17:37
• Why not write two programs? Commented Nov 14, 2017 at 17:40
• @UlrichSchwarz That is very useful information! In that case, what would no options do? Just nothing? Or print the help text? Or did you mean to say no options would not be the same as --no-blur --no-detect?
– iFreilicht
Commented Nov 14, 2017 at 17:51
• 1
@CharlesDiploma because most of the time, they are executed together. Executing them separately is a special use-case that's only useful in some specific cases.
– iFreilicht
Commented Nov 14, 2017 at 17:54
• 1
@iFreilicht if the most common action is to do both, then you should make that the default. After that, you could have --action=blur, --action=detect and --action=both and state that the default is --action=both. Or just abbreviate those to --blur, --detect and --both, so that no-one needs to complain about having to type too much... (of course, if you ever add any functions, the "both" option starts to seem odd.) But whatever you do, document the options and the default. Other than that, I think it's just up to you as the author.
– ilkkachu
Commented Nov 14, 2017 at 18:25
2 Answers 2
8
POSIX just says (regarding mutually exclusive command line options in POSIX utilities):
The use of conflicting mutually-exclusive arguments produces undefined results, unless a utility description specifies otherwise.
Some command line tools have conflicting command line options (such as both a --silent option and a --verbose option). In the case that both options are used when invoking the tool, if allowed, the last parsed option (the one last on the line) usually wins.
The last one of --blur and --detect would be used. The documentation would specify what options were exclusive.
Compare ls -l -C with ls -C -l, for example.
Other tools simply disallow conflicting command line options, giving the user a diagnostic message on the standard error stream and exiting with a non-zero exit code when such a situation occurs.
Your code would error out if both --blur and --detect were used.
This is done in e.g. cut which has conflicting flags -b, -c and -f.
Some tools may provide a different effect depending on what name it is invoked as. So, you could have two names (hard links) for your tool, one called detectface and another called blurface. These would be the exact same binary but the program would determine what name it was invoked as to figure out what operation to perform.
This is common on system where some shell masquerades as both /bin/sh (a POSIX shell) and as itself (e.g. bash on Linux, or ksh on OpenBSD) and that switches to "POSIX sh mode" when invoked as sh, or you might have a compiler that compiles both C and C++ code and switches mode depending on whether it's invoked as cc or c++, etc. (both gcc and clang does this).
1
• Very interesting info about the symlink-dependant behaviour. I think your answer really shows that mutually exclusive options are to be avoided when possible.
– iFreilicht
Commented Nov 15, 2017 at 9:47
3
I'd ask myself what the user will want the program to do in most cases and make exactly that the default behaviour. This default behaviour should be triggered automatically when no option is specified. On the other hand if there is an option specified, nothing should be done by the command unless specified with an option.
Here's a counterexample of what I consider painfully poor programming:
avconv -i file.avi
outputs some information about your video file, -i sets the input file and as there's no output specified avconv takes it you just want the info.
avconv file.avi
overwrites your precious video without any warning or doing a backup, because avconv willfully takes the argument as the output file and writes to it no matter what, even if there's nothing to write.
I think you get the point.
Here's what I'd call intuitive. If the default behaviour is
• both detect and blur:
• command and
command --detect --blur does detect and blur
• command --detect does only detect
• command --blur does only blur
• just one, e.g. for detect:
• command and
command --detect does only detect
• command --blur does only blur
• command --detect --blur does detect and blur, if you feel like this is useful there's also command --detectblur as a shorthand for this
I'd also define the short options -d and -b so that users can call command -bd to set both options no matter what the default behaviour is.
1
• 1
Yes, the default is to do both. Thanks for providing the counterexample!
– iFreilicht
Commented Nov 15, 2017 at 9:50
You must log in to answer this question.
Not the answer you're looking for? Browse other questions tagged .
|
{
"url": "https://unix.stackexchange.com/questions/404541/should-i-use-mutually-exclusive-options-on-my-command-line-tool/404674",
"source_domain": "unix.stackexchange.com",
"snapshot_id": "CC-MAIN-2024-33",
"warc_metadata": {
"Content-Length": "171041",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:IXSCL2ZOCQPYSHFDZMIQKDWCYOEJRENU",
"WARC-Concurrent-To": "<urn:uuid:ad539a2c-c3fd-4f41-8753-f9ce5e5ba53c>",
"WARC-Date": "2024-08-15T21:53:39Z",
"WARC-IP-Address": "172.64.144.30",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:UB7HRR2A34WCKX4VEIIE73JPVGPN44HQ",
"WARC-Record-ID": "<urn:uuid:ec9e2bdf-99dc-45fa-b473-41488fc95a5a>",
"WARC-Target-URI": "https://unix.stackexchange.com/questions/404541/should-i-use-mutually-exclusive-options-on-my-command-line-tool/404674",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:20e08b14-8dfa-4ef0-82ac-67e06c79ca1f>"
},
"warc_info": "isPartOf: CC-MAIN-2024-33\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for August 2024\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-186\r\nsoftware: Apache Nutch 1.20 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.5-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
2,
3,
47,
48,
298,
299,
341,
364,
385,
386,
493,
494,
696,
697,
899,
900,
902,
908,
1149,
1213,
1425,
1442,
1478,
1484,
1649,
1666,
1702,
1708,
2249,
2264,
2300,
2301,
2313,
2314,
2316,
2317,
2405,
2406,
2536,
2537,
2538,
2796,
2797,
2909,
2910,
2955,
2956,
2957,
3153,
3154,
3219,
3220,
3288,
3289,
3290,
3619,
3620,
3983,
3984,
3986,
4149,
4166,
4201,
4203,
4204,
4528,
4529,
4530,
4601,
4602,
4621,
4622,
4768,
4769,
4785,
4786,
4986,
4987,
5014,
5015,
5016,
5076,
5077,
5103,
5121,
5172,
5212,
5248,
5279,
5297,
5337,
5373,
5515,
5516,
5656,
5657,
5659,
5665,
5742,
5759,
5794,
5795,
5836,
5837
],
"line_end_idx": [
2,
3,
47,
48,
298,
299,
341,
364,
385,
386,
493,
494,
696,
697,
899,
900,
902,
908,
1149,
1213,
1425,
1442,
1478,
1484,
1649,
1666,
1702,
1708,
2249,
2264,
2300,
2301,
2313,
2314,
2316,
2317,
2405,
2406,
2536,
2537,
2538,
2796,
2797,
2909,
2910,
2955,
2956,
2957,
3153,
3154,
3219,
3220,
3288,
3289,
3290,
3619,
3620,
3983,
3984,
3986,
4149,
4166,
4201,
4203,
4204,
4528,
4529,
4530,
4601,
4602,
4621,
4622,
4768,
4769,
4785,
4786,
4986,
4987,
5014,
5015,
5016,
5076,
5077,
5103,
5121,
5172,
5212,
5248,
5279,
5297,
5337,
5373,
5515,
5516,
5656,
5657,
5659,
5665,
5742,
5759,
5794,
5795,
5836,
5837,
5903
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 5903,
"ccnet_original_nlines": 104,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.42789599299430847,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.018912529572844505,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.22695034742355347,
"rps_doc_frac_unique_words": 0.37074148654937744,
"rps_doc_mean_word_length": 4.4899797439575195,
"rps_doc_num_sentences": 62,
"rps_doc_symbol_to_word_ratio": 0.0007880200282670557,
"rps_doc_unigram_entropy": 5.339099407196045,
"rps_doc_word_count": 998,
"rps_doc_frac_chars_dupe_10grams": 0.023209109902381897,
"rps_doc_frac_chars_dupe_5grams": 0.08748047053813934,
"rps_doc_frac_chars_dupe_6grams": 0.06605668365955353,
"rps_doc_frac_chars_dupe_7grams": 0.06605668365955353,
"rps_doc_frac_chars_dupe_8grams": 0.023209109902381897,
"rps_doc_frac_chars_dupe_9grams": 0.023209109902381897,
"rps_doc_frac_chars_top_2gram": 0.018745819106698036,
"rps_doc_frac_chars_top_3gram": 0.015621510334312916,
"rps_doc_frac_chars_top_4gram": 0.020084800198674202,
"rps_doc_books_importance": -483.83953857421875,
"rps_doc_books_importance_length_correction": -483.83953857421875,
"rps_doc_openwebtext_importance": -313.8830871582031,
"rps_doc_openwebtext_importance_length_correction": -313.8830871582031,
"rps_doc_wikipedia_importance": -213.1231689453125,
"rps_doc_wikipedia_importance_length_correction": -213.1231689453125
},
"fasttext": {
"dclm": 0.254910945892334,
"english": 0.9142876267433167,
"fineweb_edu_approx": 2.0647623538970947,
"eai_general_math": 0.8953195214271545,
"eai_open_web_math": 0.48387980461120605,
"eai_web_code": 0.7080520987510681
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.445",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "4",
"label": "Analyze"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "6",
"label": "Indeterminate"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-1,344,851,905,018,223,600
|
• Status: Solved
• Priority: Medium
• Security: Public
• Views: 667
• Last Modified:
flood detection
I have a php poll script in my website, and there's some idiot that uses some Perl/Java/script kiddie tool to post the script in a loop and manipulate the poll results.
How can I detect his flood through the script and ignore the post?
Until now the script would plant a cookie when you vote and if you try to vote again it would check if the cookie exists and if so it will ignore the vote, because the flooder uses some tool and not a browser the cookie is not planted...
The flooder uses more than one shell account to run his posting script so the IP's are different.
What can I do to detect the flooder and ignore him?
0
socket9001
Asked:
socket9001
• 3
• 3
• 2
• +2
1 Solution
dkjariwalaCommented:
There can not be 100% fullproof way.
But few things you can try,
Ok, users need to create an account with an email not in the database. The person also has to verify this email to become a member.
You need to be a member to vote in the poll.
The poll script logs ip, and it won't allow voting from the same ip for next 10 minutes. [You have to do this cause IP doesnt remain same all the time for users.]
It also uses cookies.
So to vote more than once, the person has to create a new account with a new email (and have to create a new email account if they don't have others), and then go to that email to verify.
The person has to change his ip.
He has to delete his cookies if he had the cookie option on. He has to log out or close the browser to clear his sessions, log in to his new account, and vote.
That is the best you can do to avoid flooding.
JD
0
andrivCommented:
Excellent idea with having to verify e-mail JD!!! This way they can't just register using just any e-mail just for the sake of gaining access!! They have to apply then reply to the auto emial to become a member then you can limit each email to one vote a day.
Good Job JD.
0
dkjariwalaCommented:
Thx Andriv.
JD
0
[Webinar] Kill tickets & tabs using PowerShell
Are you tired of cycling through the same browser tabs everyday to close the same repetitive tickets? In this webinar JumpCloud will show how you can leverage RESTful APIs to build your own PowerShell modules to kill tickets & tabs using the PowerShell command Invoke-RestMethod.
Richard QuadlingSenior Software DeveloperCommented:
Just to clear something in my own mind ...
1 - The user comes to the site, wishing to register and enters username/password/email address.
2 - The registration process sends out an email telling them to enter a code (which is logged against with the email address).
3 - The user then has a confirmed account.
They have to login to your site to vote (members only sort of thing).
When they have voted, you could log their account ID against the vote, so you can instantly stop them from multiple voting, or allow them to amend their vote (wouldn't that be great in the real world?!? You don't like your president/prime minister/whoever and you can change your mind retrospectively! Ha!).
That looks quite secure. Did I miss anything?
Regards,
Richard Quadling.
0
dkjariwalaCommented:
Thats precisely what you should be doing.
All the best,
JD
0
andrivCommented:
It doesn't even have to be a code, if they respond to the e-mail then you know it is there own and the registration is completed.
Now that they are registered they only can have one vote per day for that paticular e-mail address.
Experts-exchange does it as well. In order for you registration to be completed and before you can gain access you must confirm to the auto-email they send you.
No one can register with a fake e-mail address. Sure people can register many e-mail address for the sake of registering but that is forcing them to do a lot more work to manipulate the system and their program must enter each email address only once. So if they wanted their program to do multiple vote submission they can only do it once for each account.
0
LexZEUSCommented:
poll flooding..
one way is to use session to prevent flooding..
Main.php -> to display the poll
<?
session_start();
session_register("pool_id");
// the poll id
$poll_id = 123;
// display the poll ..
include("PollDisplay.php");
?>
SubmitPool.php -> to submit the poll
<?
session_start();
// take poll_id from session, since there is possibility
// that user hardcode poll_id=xxx in url
if ($HTTP_VAR_SESSION["poll_id"]=="")
{
header("Location: Main.php");
print "Ah.. you never visit the first page!\n";
exit;
}
// assuming poll_id taken from session is 123
// check whether variable $make_choice_already_for_123
// is valued with "yes" or not:
session_register("make_choice_already_for_".$poll_id);
if (${"make_choice_already_for_".$poll_id} == "yes")
{
die ("You have participated in poll before!");
}
// mark current user already participated in poll 123
${"make_choice_already_for_".$poll_id} = "yes";
include("PollProcess.php");
?>
Ideally you can *ONLY* submit your choice *IF* you have seen the poll. Then we can *assume* that user *MUST* go to Main.php before submit the poll.
You can combine this code with your setCookie to prevent user to reparticipate in poll in the next hours/day (as the session expired). User can delete your cookie though, but this mechanism make flooding harder: you will have to go to first page with new session in order you can participate in poll..
0
LexZEUSCommented:
in my last sentence:
you will have to go to first page with new session in order you can participate in poll..
what i mean is:
Someone will have to access the first page (with new session) in order to participate in poll.
rgds,
Alex
0
ibishopCommented:
I guess it depends on whether you're taking a semi-anonymous poll, or one where the vote is clearly identifiable to an account.
For identifiable - the above work great.
For semi-anonymous, I generally create a composite string, comprising The IP Address, the Date part of the timestamp, and something else (for example, the name of the poll), structured similar to :
MyPoll-192.168.0.11-20020327
By inserting that into a field requiring Unique values, you can limit to one vote per IP per Poll per Day.
This does have some limitations with proxy servers etc., but is pretty effective - I've only ever had a limited number of complaints regarding my semi-anonymous polls using this method.
Best regards,
Ian
0
LexZEUSCommented:
if you will use date approach you may synchronize it with GMT for you may reside in US, whereas I am in Asia Pacific :) ..
>MyPoll-192.168.0.11-20020327
192.168.xxx.xxx?? You are globalsources people! OMG!!
0
Featured Post
[Webinar] Kill tickets & tabs using PowerShell
Are you tired of cycling through the same browser tabs everyday to close the same repetitive tickets? In this webinar JumpCloud will show how you can leverage RESTful APIs to build your own PowerShell modules to kill tickets & tabs using the PowerShell command Invoke-RestMethod.
• 3
• 3
• 2
• +2
Tackle projects and never again get stuck behind a technical roadblock.
Join Now
|
{
"url": "https://www.experts-exchange.com/questions/20280608/flood-detection.html",
"source_domain": "www.experts-exchange.com",
"snapshot_id": "crawl=CC-MAIN-2018-09",
"warc_metadata": {
"Content-Length": "123187",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:3WCI2SWOYVUEMMJB4OXDPBK5MWRM3QH3",
"WARC-Concurrent-To": "<urn:uuid:31487da7-97ab-4bdf-9583-11dd06a9a907>",
"WARC-Date": "2018-02-22T23:11:10Z",
"WARC-IP-Address": "104.20.168.10",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:NULUOJOHHHHJAITTLAD4RSVLQBSTFLWQ",
"WARC-Record-ID": "<urn:uuid:6934e902-6f0f-4600-85d7-41a16adb2803>",
"WARC-Target-URI": "https://www.experts-exchange.com/questions/20280608/flood-detection.html",
"WARC-Truncated": "length",
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:67c8a184-2ebb-4bb5-b35d-aa16ff6bcdf2>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-180-204-196.ec2.internal\r\nsoftware: Nutch 1.6 (CC)\r\nisPartOf: CC-MAIN-2018-09\r\noperator: Common Crawl Admin\r\ndescription: Wide crawl of the web for February 2018\r\npublisher: Common Crawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
19,
40,
61,
76,
95,
96,
112,
113,
282,
349,
587,
685,
686,
738,
740,
751,
758,
769,
775,
781,
787,
794,
805,
807,
828,
865,
893,
894,
1026,
1071,
1072,
1235,
1236,
1258,
1259,
1260,
1448,
1481,
1641,
1642,
1689,
1690,
1693,
1695,
1697,
1714,
1974,
1975,
1988,
1990,
1992,
2013,
2025,
2026,
2029,
2031,
2078,
2079,
2359,
2360,
2362,
2414,
2457,
2458,
2554,
2555,
2682,
2683,
2726,
2727,
2797,
2798,
3106,
3107,
3153,
3154,
3163,
3164,
3182,
3184,
3186,
3207,
3249,
3250,
3264,
3267,
3269,
3271,
3288,
3418,
3419,
3519,
3520,
3682,
3683,
4041,
4043,
4045,
4063,
4079,
4080,
4128,
4129,
4161,
4164,
4181,
4210,
4225,
4241,
4242,
4265,
4293,
4296,
4297,
4334,
4337,
4354,
4411,
4452,
4490,
4495,
4528,
4579,
4588,
4593,
4594,
4640,
4695,
4727,
4782,
4835,
4840,
4890,
4895,
4896,
4950,
4998,
5026,
5029,
5030,
5031,
5179,
5481,
5483,
5485,
5503,
5524,
5614,
5615,
5631,
5726,
5727,
5733,
5734,
5739,
5741,
5743,
5761,
5889,
5890,
5931,
5932,
6130,
6131,
6160,
6161,
6268,
6269,
6455,
6456,
6470,
6471,
6475,
6477,
6479,
6497,
6620,
6621,
6622,
6652,
6653,
6707,
6709,
6710,
6724,
6725,
6772,
6773,
7053,
7054,
7060,
7066,
7072,
7079,
7151
],
"line_end_idx": [
19,
40,
61,
76,
95,
96,
112,
113,
282,
349,
587,
685,
686,
738,
740,
751,
758,
769,
775,
781,
787,
794,
805,
807,
828,
865,
893,
894,
1026,
1071,
1072,
1235,
1236,
1258,
1259,
1260,
1448,
1481,
1641,
1642,
1689,
1690,
1693,
1695,
1697,
1714,
1974,
1975,
1988,
1990,
1992,
2013,
2025,
2026,
2029,
2031,
2078,
2079,
2359,
2360,
2362,
2414,
2457,
2458,
2554,
2555,
2682,
2683,
2726,
2727,
2797,
2798,
3106,
3107,
3153,
3154,
3163,
3164,
3182,
3184,
3186,
3207,
3249,
3250,
3264,
3267,
3269,
3271,
3288,
3418,
3419,
3519,
3520,
3682,
3683,
4041,
4043,
4045,
4063,
4079,
4080,
4128,
4129,
4161,
4164,
4181,
4210,
4225,
4241,
4242,
4265,
4293,
4296,
4297,
4334,
4337,
4354,
4411,
4452,
4490,
4495,
4528,
4579,
4588,
4593,
4594,
4640,
4695,
4727,
4782,
4835,
4840,
4890,
4895,
4896,
4950,
4998,
5026,
5029,
5030,
5031,
5179,
5481,
5483,
5485,
5503,
5524,
5614,
5615,
5631,
5726,
5727,
5733,
5734,
5739,
5741,
5743,
5761,
5889,
5890,
5931,
5932,
6130,
6131,
6160,
6161,
6268,
6269,
6455,
6456,
6470,
6471,
6475,
6477,
6479,
6497,
6620,
6621,
6622,
6652,
6653,
6707,
6709,
6710,
6724,
6725,
6772,
6773,
7053,
7054,
7060,
7066,
7072,
7079,
7151,
7159
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 7159,
"ccnet_original_nlines": 195,
"rps_doc_curly_bracket": 0.0011174699757248163,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.4064171016216278,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.01671122945845127,
"rps_doc_frac_lines_end_with_ellipsis": 0.010204079560935497,
"rps_doc_frac_no_alph_words": 0.20922459661960602,
"rps_doc_frac_unique_words": 0.3508920967578888,
"rps_doc_mean_word_length": 4.628716945648193,
"rps_doc_num_sentences": 90,
"rps_doc_symbol_to_word_ratio": 0.0013369000516831875,
"rps_doc_unigram_entropy": 5.3480072021484375,
"rps_doc_word_count": 1177,
"rps_doc_frac_chars_dupe_10grams": 0.12408223003149033,
"rps_doc_frac_chars_dupe_5grams": 0.13252569735050201,
"rps_doc_frac_chars_dupe_6grams": 0.13252569735050201,
"rps_doc_frac_chars_dupe_7grams": 0.13252569735050201,
"rps_doc_frac_chars_dupe_8grams": 0.12701909244060516,
"rps_doc_frac_chars_dupe_9grams": 0.12408223003149033,
"rps_doc_frac_chars_top_2gram": 0.014317180030047894,
"rps_doc_frac_chars_top_3gram": 0.0022026400547474623,
"rps_doc_frac_chars_top_4gram": 0.014684289693832397,
"rps_doc_books_importance": -531.5816040039062,
"rps_doc_books_importance_length_correction": -531.5816040039062,
"rps_doc_openwebtext_importance": -328.71954345703125,
"rps_doc_openwebtext_importance_length_correction": -328.71954345703125,
"rps_doc_wikipedia_importance": -190.19546508789062,
"rps_doc_wikipedia_importance_length_correction": -190.19546508789062
},
"fasttext": {
"dclm": 0.04470402002334595,
"english": 0.9170750975608826,
"fineweb_edu_approx": 1.2763962745666504,
"eai_general_math": 0.028567969799041748,
"eai_open_web_math": 0.12137514352798462,
"eai_web_code": 0.009515110403299332
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.82",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.678",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "4",
"label": "Analyze"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-8,096,101,483,800,004,000
|
Avatar: Republic City Roleplay
Very Important; Please look over before anything else.
Share
avatar
Sergetank
Admin
Posts : 22
Join date : 2012-10-30
Age : 103
Location : The Void
Very Important; Please look over before anything else.
Post Sergetank on Tue Oct 30, 2012 9:30 pm
This is a roleplay based on Byond / RolePlayUnlimited. This is, basically, a forum for a roleplay that happens on something else. In order to roleplay, you will need to download these two things.
Byond Download
RPUnlimited
If you're concerned about system requirements, don't be. This rig that yours truly is using is from 2002 and dusty as hell. And bad, really bad. Skype can't even run on this thing.
Yet RPU and Byond can. Take that as you will. Interestingly enough though, I've been alerted that it doesn't work on Macs. Hue.
Here's a step by step process of how to set up Byond and RPU on your computer.
1. You click the first hotlink 'Byond Download' and you should find something that looks like this:
Either the Beta or the Stable will work fine for RPU.
2. Once you have it installed, you also need to create a 'key'. Aka, a username. It's easy, but requires an e-mail confirmation. Isn't it lovely?
Once that's done you should get this:
2. Once you've made a key, you can log in and explore RPU. ( Brace yourselves. )
3. You click the second link, 'RPUnlimited' and find the Avatar RP from the list of servers available.
4. Once you start to log in, it'll take you to the title page.
5. Click the hell out of 'Load Data'. Creating new leads you down this empty process that takes forever and doesn't do anything. Thank AnthonyHawkina for that vital part of the update. Once you get in the server looks like this:
That's our lovely Sentinel Prime giving her typical greeting, don't worry.
From there on out, you should be set. And welcome to the roleplay~
Current date/time is Tue Jan 22, 2019 9:53 am
|
{
"url": "http://republic-city.forumotion.com/t3-very-important-please-look-over-before-anything-else",
"source_domain": "republic-city.forumotion.com",
"snapshot_id": "crawl=CC-MAIN-2019-04",
"warc_metadata": {
"Content-Length": "34063",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:4RCDK4KQ2XA3ZJH2RZVUHX2INVWDQ4YB",
"WARC-Concurrent-To": "<urn:uuid:2dc3f950-214c-4863-a07a-234a063bfa67>",
"WARC-Date": "2019-01-22T12:53:41Z",
"WARC-IP-Address": "94.23.150.222",
"WARC-Identified-Payload-Type": "application/xhtml+xml",
"WARC-Payload-Digest": "sha1:QKYNKPJZO73I22TWB776K6CXGPLX5RIX",
"WARC-Record-ID": "<urn:uuid:5609f41f-504e-479e-b296-4061b2161eee>",
"WARC-Target-URI": "http://republic-city.forumotion.com/t3-very-important-please-look-over-before-anything-else",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:6a84ddf5-b081-4d48-84de-9cf2081634ba>"
},
"warc_info": "isPartOf: CC-MAIN-2019-04\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for January 2019\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-140-252-72.ec2.internal\r\nsoftware: Apache Nutch 1.15 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 0.11-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
31,
32,
91,
92,
102,
113,
127,
137,
138,
153,
180,
194,
218,
219,
278,
279,
327,
328,
329,
529,
530,
549,
550,
566,
567,
752,
753,
885,
886,
969,
970,
1074,
1132,
1133,
1283,
1284,
1326,
1327,
1412,
1413,
1520,
1521,
1522,
1589,
1590,
1823,
1824,
1903,
1904,
1975,
1976,
1977
],
"line_end_idx": [
31,
32,
91,
92,
102,
113,
127,
137,
138,
153,
180,
194,
218,
219,
278,
279,
327,
328,
329,
529,
530,
549,
550,
566,
567,
752,
753,
885,
886,
969,
970,
1074,
1132,
1133,
1283,
1284,
1326,
1327,
1412,
1413,
1520,
1521,
1522,
1589,
1590,
1823,
1824,
1903,
1904,
1975,
1976,
1977,
2028
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 2028,
"ccnet_original_nlines": 52,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.38513514399528503,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.01351351011544466,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.2477477490901947,
"rps_doc_frac_unique_words": 0.57485032081604,
"rps_doc_mean_word_length": 4.36227560043335,
"rps_doc_num_sentences": 35,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.953121662139893,
"rps_doc_word_count": 334,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.061770759522914886,
"rps_doc_frac_chars_dupe_6grams": 0.061770759522914886,
"rps_doc_frac_chars_dupe_7grams": 0.061770759522914886,
"rps_doc_frac_chars_dupe_8grams": 0.061770759522914886,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.01647219993174076,
"rps_doc_frac_chars_top_3gram": 0.026080990210175514,
"rps_doc_frac_chars_top_4gram": 0.03157171979546547,
"rps_doc_books_importance": -225.01022338867188,
"rps_doc_books_importance_length_correction": -225.01022338867188,
"rps_doc_openwebtext_importance": -149.01467895507812,
"rps_doc_openwebtext_importance_length_correction": -149.01467895507812,
"rps_doc_wikipedia_importance": -129.50172424316406,
"rps_doc_wikipedia_importance_length_correction": -129.50172424316406
},
"fasttext": {
"dclm": 0.19209390878677368,
"english": 0.9242660999298096,
"fineweb_edu_approx": 1.2539479732513428,
"eai_general_math": 0.06221640110015869,
"eai_open_web_math": 0.28138047456741333,
"eai_web_code": 0.004175359848886728
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.6",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "794.8",
"labels": {
"level_1": "Arts",
"level_2": "Amusements and Recreation",
"level_3": ""
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "5",
"label": "Social/Forum"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "4",
"label": "Missing Images or Figures"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "23",
"label": "Tutorial"
},
"secondary": {
"code": "21",
"label": "Customer Support"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "1",
"label": "No Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "1",
"label": "General Audience"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-7,822,654,732,965,603,000
|
Blob Blame History Raw
#!/bin/bash
# Copyright (C) 1999 - 2004 Red Hat, Inc. All rights reserved. This
# copyrighted material is made available to anyone wishing to use, modify,
# copy, or redistribute it subject to the terms and conditions of the
# GNU General Public License version 2.
#
# You should have received a copy of the GNU General Public License
# along with this program; if not, write to the Free Software
# Foundation, Inc., 675 Mass Ave, Cambridge, MA 02139, USA.
# redirect errors to a file in user's home directory if we can
if [ -z "$GDMSESSION" ]; then
# GDM redirect output itself in a smarter fashion
errfile="$HOME/.xsession-errors"
if ( umask 077 && cp /dev/null "$errfile" 2> /dev/null ); then
chmod 600 "$errfile"
[ -x /sbin/restorecon ] && /sbin/restorecon $errfile
exec > "$errfile" 2>&1
else
errfile=$(mktemp -q /tmp/xses-$USER.XXXXXX)
if [ $? -eq 0 ]; then
exec > "$errfile" 2>&1
fi
fi
fi
SWITCHDESKPATH=/usr/share/switchdesk
# Mandatorily source xinitrc-common, which is common code shared between the
# Xsession and xinitrc scripts which has been factored out to avoid duplication
. /etc/X11/xinit/xinitrc-common
# This Xsession.d implementation, is intended to obsolte and replace the
# various mechanisms present in the 'case' statement which follows, and to
# eventually be able to easily remove all hard coded window manager specific
# content from this script. See bug #142260 for additional explanation and
# details. All window manager rpm packages and desktop environment
# packages should be modified to provide the Xsession.d/Xsession.$wm scripts
# to start themselves up. In the future, the legacy switchdesk mechanisms
# and hard coded window managers and desktop environments will be removed from
# this script.
XCLIENTS_D=/etc/X11/xinit/Xclients.d
if [ "$#" -eq 1 ] && [ -x "$XCLIENTS_D/Xclients.$1.sh" ]; then
exec -l $SHELL -c "$CK_XINIT_SESSION $SSH_AGENT $XCLIENTS_D/Xclients.$1.sh"
else
# now, we see if xdm/gdm/kdm has asked for a specific environment
case $# in
1)
if [ -x "$SWITCHDESKPATH/Xclients.$1" ]; then
exec -l $SHELL -c "$SWITCHDESKPATH/Xclients.$1";
fi;
case "$1" in
failsafe)
exec -l $SHELL -c "xterm -geometry 80x24-0-0"
;;
gnome|gnome-session)
# lack of SSH_AGENT is intentional, see #441123. though
# the whole thing should really happen in xinitrc.d anyway.
exec -l $SHELL -c gnome-session
exec /bin/sh -c "exec -l $SHELL -c \"gnome-session\""
;;
kde|kde1|kde2)
exec $CK_XINIT_SESSION $SSH_AGENT /bin/sh -c "exec -l $SHELL -c \"startkde\""
;;
twm)
# fall back to twm
exec $CK_XINIT_SESSION $SSH_AGENT /bin/sh -c "exec -l $SHELL -c \"twm\""
;;
*)
# GDM provies either a command line as the first argument or
# provides 'failsafe', 'default' or 'custom'. KDM will do the
# same at some point
if [ "$1" != "default" -a "$1" != "custom" ]; then
exec $CK_XINIT_SESSION $SSH_AGENT /bin/sh -c "exec -l $SHELL -c \"$1\""
fi
;;
esac
esac
fi
# otherwise, take default action
if [ -x "$HOME/.xsession" ]; then
exec -l $SHELL -c "$CK_XINIT_SESSION $SSH_AGENT $HOME/.xsession"
elif [ -x "$HOME/.Xclients" ]; then
exec -l $SHELL -c "$CK_XINIT_SESSION $SSH_AGENT $HOME/.Xclients"
elif [ -x /etc/X11/xinit/Xclients ]; then
exec -l $SHELL -c "$CK_XINIT_SESSION $SSH_AGENT /etc/X11/xinit/Xclients"
else
# should never get here; failsafe fallback
exec -l $SHELL -c "xsm"
fi
|
{
"url": "https://git.centos.org/rpms/xorg-x11-xinit/blob/c7/f/SOURCES/Xsession",
"source_domain": "git.centos.org",
"snapshot_id": "CC-MAIN-2023-40",
"warc_metadata": {
"Content-Length": "18662",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:JKWRENCR7SBCA6AWS46EKXSPNWZXEPDT",
"WARC-Concurrent-To": "<urn:uuid:fced643d-7dac-427f-b694-8b151243c50d>",
"WARC-Date": "2023-10-03T06:45:05Z",
"WARC-IP-Address": "8.43.84.211",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:WIB3ZITWELF2LSLVJOGIKRKNWFYKJRPP",
"WARC-Record-ID": "<urn:uuid:a9b7c9db-a44d-4974-9209-74121d5dff18>",
"WARC-Target-URI": "https://git.centos.org/rpms/xorg-x11-xinit/blob/c7/f/SOURCES/Xsession",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:596d592e-9848-429e-b04a-c7365a632692>"
},
"warc_info": "isPartOf: CC-MAIN-2023-40\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for September/October 2023\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-200\r\nsoftware: Apache Nutch 1.19 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.5-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
23,
35,
103,
178,
248,
288,
290,
358,
420,
480,
481,
544,
574,
628,
665,
732,
761,
822,
853,
862,
914,
944,
979,
990,
997,
1000,
1001,
1038,
1039,
1116,
1196,
1228,
1229,
1302,
1377,
1454,
1530,
1598,
1675,
1750,
1829,
1845,
1882,
1945,
2025,
2030,
2096,
2107,
2110,
2160,
2216,
2224,
2225,
2242,
2253,
2304,
2312,
2334,
2396,
2461,
2498,
2558,
2566,
2582,
2665,
2673,
2679,
2706,
2784,
2792,
2796,
2864,
2934,
2962,
3018,
3092,
3100,
3108,
3117,
3122,
3125,
3126,
3159,
3193,
3262,
3298,
3367,
3409,
3486,
3491,
3538,
3566
],
"line_end_idx": [
23,
35,
103,
178,
248,
288,
290,
358,
420,
480,
481,
544,
574,
628,
665,
732,
761,
822,
853,
862,
914,
944,
979,
990,
997,
1000,
1001,
1038,
1039,
1116,
1196,
1228,
1229,
1302,
1377,
1454,
1530,
1598,
1675,
1750,
1829,
1845,
1882,
1945,
2025,
2030,
2096,
2107,
2110,
2160,
2216,
2224,
2225,
2242,
2253,
2304,
2312,
2334,
2396,
2461,
2498,
2558,
2566,
2582,
2665,
2673,
2679,
2706,
2784,
2792,
2796,
2864,
2934,
2962,
3018,
3092,
3100,
3108,
3117,
3122,
3125,
3126,
3159,
3193,
3262,
3298,
3367,
3409,
3486,
3491,
3538,
3566,
3568
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 3568,
"ccnet_original_nlines": 92,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.22035928070545197,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.06347305327653885,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.41556885838508606,
"rps_doc_frac_unique_words": 0.5089285969734192,
"rps_doc_mean_word_length": 5.3125,
"rps_doc_num_sentences": 35,
"rps_doc_symbol_to_word_ratio": 0.041916169226169586,
"rps_doc_unigram_entropy": 4.998201847076416,
"rps_doc_word_count": 448,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.16806723177433014,
"rps_doc_frac_chars_dupe_6grams": 0.14705881476402283,
"rps_doc_frac_chars_dupe_7grams": 0.1163865476846695,
"rps_doc_frac_chars_dupe_8grams": 0.05420168116688728,
"rps_doc_frac_chars_dupe_9grams": 0.05420168116688728,
"rps_doc_frac_chars_top_2gram": 0.025210080668330193,
"rps_doc_frac_chars_top_3gram": 0.05042016878724098,
"rps_doc_frac_chars_top_4gram": 0.05546218156814575,
"rps_doc_books_importance": -444.83026123046875,
"rps_doc_books_importance_length_correction": -444.83026123046875,
"rps_doc_openwebtext_importance": -255.05645751953125,
"rps_doc_openwebtext_importance_length_correction": -255.05645751953125,
"rps_doc_wikipedia_importance": -202.34701538085938,
"rps_doc_wikipedia_importance_length_correction": -202.34701538085938
},
"fasttext": {
"dclm": 0.06589806079864502,
"english": 0.7023371458053589,
"fineweb_edu_approx": 1.8999278545379639,
"eai_general_math": 0.8171319961547852,
"eai_open_web_math": 0.1416652798652649,
"eai_web_code": 0.48873376846313477
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.445",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.02",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "4",
"label": "Code/Software"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "21",
"label": "Customer Support"
}
},
"reasoning_depth": {
"primary": {
"code": "4",
"label": "Advanced Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "4",
"label": "Graduate/Expert Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-6,409,354,930,604,276,000
|
Search:
Type: Posts; User: rtumatt
Search: Search took 0.24 seconds.
1. need help with 'org.apache.commons.net.ftp.FTPClient'
I have this code which uploads to my ftp server fine however i am unable to return a value of how far the file has uploaded, any help would be appreciated thanks.
code:
import...
2. Replies
2
Views
1,108
Re: IllegalArgumentException: Pan not supported
Pan is something to do with the audio like panning sound i think. Nothing in my actual code
3. Replies
2
Views
1,108
IllegalArgumentException: Pan not supported
My program plays wav files, under windows this works fine but i am now developing the application on my Ubuntu 10.4 machine and with the same source code i get the error:
Exception in thread...
4. Replies
2
Views
2,180
Re: Create buttons at runtime
That helped me out more than you can imagine, thankyou! i have the problem of the positioning of the buttons now all being ontop of each other :S
5. Replies
1
Views
1,979
Re: how to merge my OO with GUI
Hi Firstly to get to grips with GUI's use netbeans or eclipse (with the jigloo GUI plugin) What you then aim to do is call methods just like you would in your main program. To do this you could add...
6. Replies
2
Views
2,180
Create buttons at runtime
Hello all I am trying to read for example 4 html files from a directory then at runtime the buttons are created (this is important as at runtime there could be 5 html files etc) which will correspond...
7. Re: how do I keep a persistent prompt in JTextArea and allow user input
import java.util.Scanner;
declare the following in your constructor:
source = new Scanner(System.in);
declare the variable:
private Scanner source;
8. Jigloo help to produce a text area which only scrolls down
Hi i would like to know how to make a text area in Jigloo and have it only scroll down. There should be the option to set expands horizontal to false but i am unable to find this setting. Thankyou
9. Replies
3
Views
1,209
Re: Adding to Array from JavaSpace problem
thankyou for the reply. I have been reading alot on JavaSpaces, turns out to treat objects as if they were in an array you need to write a head and tail object to space to keep track, i thought this...
10. Replies
2
Views
728
Adding to Array from JavaSpace problem
Not sure if this is advanced or not but here goes:
I'm now stuck on such a simple task I have no idea what to do. I just want to take from the space all "chatRooms" then extract the chat room name...
11. Replies
3
Views
1,209
Adding to Array from JavaSpace problem
I'm now stuck on such a simple task I have no idea what to do. I just want to take from the space all "chatRooms" then extract the chat room name which i will keep in an array, then write to the...
Results 1 to 11 of 11
|
{
"url": "http://www.javaprogrammingforums.com/search.php?s=a7408ed530330627c3dea8f937471d80&searchid=705132",
"source_domain": "www.javaprogrammingforums.com",
"snapshot_id": "crawl=CC-MAIN-2013-48",
"warc_metadata": {
"Content-Length": "31528",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:XQCSKCBIFLYLGKF7IUEVAHEYA4I4F6GV",
"WARC-Concurrent-To": "<urn:uuid:32f8da07-e181-4132-b1d9-2d1aecbd742e>",
"WARC-Date": "2013-12-12T20:03:58Z",
"WARC-IP-Address": "198.57.186.242",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:CT6MHPJSACFYYBUUEEK5CQT7AORYB2II",
"WARC-Record-ID": "<urn:uuid:7c8954aa-12d0-437c-8127-e0c6ae0d9c82>",
"WARC-Target-URI": "http://www.javaprogrammingforums.com/search.php?s=a7408ed530330627c3dea8f937471d80&searchid=705132",
"WARC-Truncated": "length",
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:29a8f5e7-0e3c-48af-b348-e9a96ec4c856>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-33-133-15.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2013-48\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web with URLs provided by Blekko for Winter 2013\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
8,
9,
36,
37,
71,
72,
131,
132,
299,
300,
310,
324,
337,
343,
353,
363,
364,
416,
417,
513,
526,
532,
542,
552,
553,
601,
602,
777,
778,
805,
818,
824,
834,
844,
845,
879,
880,
1030,
1043,
1049,
1059,
1069,
1070,
1106,
1107,
1312,
1325,
1331,
1341,
1351,
1352,
1382,
1383,
1590,
1667,
1668,
1698,
1699,
1746,
1747,
1748,
1785,
1786,
1812,
1813,
1841,
1905,
1906,
2107,
2120,
2126,
2136,
2146,
2147,
2194,
2195,
2401,
2415,
2421,
2431,
2439,
2440,
2483,
2484,
2539,
2540,
2693,
2707,
2713,
2723,
2733,
2734,
2777,
2778,
2980
],
"line_end_idx": [
8,
9,
36,
37,
71,
72,
131,
132,
299,
300,
310,
324,
337,
343,
353,
363,
364,
416,
417,
513,
526,
532,
542,
552,
553,
601,
602,
777,
778,
805,
818,
824,
834,
844,
845,
879,
880,
1030,
1043,
1049,
1059,
1069,
1070,
1106,
1107,
1312,
1325,
1331,
1341,
1351,
1352,
1382,
1383,
1590,
1667,
1668,
1698,
1699,
1746,
1747,
1748,
1785,
1786,
1812,
1813,
1841,
1905,
1906,
2107,
2120,
2126,
2136,
2146,
2147,
2194,
2195,
2401,
2415,
2421,
2431,
2439,
2440,
2483,
2484,
2539,
2540,
2693,
2707,
2713,
2723,
2733,
2734,
2777,
2778,
2980,
3001
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 3001,
"ccnet_original_nlines": 95,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.421138197183609,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.024390239268541336,
"rps_doc_frac_lines_end_with_ellipsis": 0.0729166716337204,
"rps_doc_frac_no_alph_words": 0.21138210594654083,
"rps_doc_frac_unique_words": 0.45956605672836304,
"rps_doc_mean_word_length": 4.21301794052124,
"rps_doc_num_sentences": 39,
"rps_doc_symbol_to_word_ratio": 0.01138211041688919,
"rps_doc_unigram_entropy": 5.065391540527344,
"rps_doc_word_count": 507,
"rps_doc_frac_chars_dupe_10grams": 0.10393258184194565,
"rps_doc_frac_chars_dupe_5grams": 0.1502808928489685,
"rps_doc_frac_chars_dupe_6grams": 0.1502808928489685,
"rps_doc_frac_chars_dupe_7grams": 0.10393258184194565,
"rps_doc_frac_chars_dupe_8grams": 0.10393258184194565,
"rps_doc_frac_chars_dupe_9grams": 0.10393258184194565,
"rps_doc_frac_chars_top_2gram": 0.011704119853675365,
"rps_doc_frac_chars_top_3gram": 0.030430709943175316,
"rps_doc_frac_chars_top_4gram": 0.023876400664448738,
"rps_doc_books_importance": -248.8115692138672,
"rps_doc_books_importance_length_correction": -248.8115692138672,
"rps_doc_openwebtext_importance": -137.5282745361328,
"rps_doc_openwebtext_importance_length_correction": -137.5282745361328,
"rps_doc_wikipedia_importance": -69.36714172363281,
"rps_doc_wikipedia_importance_length_correction": -69.36714172363281
},
"fasttext": {
"dclm": 0.0233803391456604,
"english": 0.9175825119018555,
"fineweb_edu_approx": 1.3385167121887207,
"eai_general_math": 0.48945510387420654,
"eai_open_web_math": 0.26053857803344727,
"eai_web_code": 0.07356488704681396
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.133",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "2",
"label": "Click Here References"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "21",
"label": "Customer Support"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "2",
"label": "Partially Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-4,620,081,804,592,656,000
|
[HNOI2001]遥控赛车比赛
题目描述
全国遥控赛车大赛近日在星沙举行。竞赛选用一块大小为N×M的场地作为竞赛场地,要求选手的赛车在最短的时间内从起点移动到终点。虽然赛场地形高低有少许的起伏,但并不存在无法到达的地点。但是在赛场上增加了许多无法穿越的障碍物,若赛车在到达终点前撞上障碍物,就视为任务失败。 在赛车的马力和灵活性等性能相差较小的情况下,要控制速度极快的赛车绕开障碍物移动到终点,关键是提高选手的反应灵敏度,即两次改变赛车运动方向所间隔的最短时间,也可称为选手的反应时间。使自己能够更快地控制赛车改变前进的方向。 当然,由于选手反应灵敏度的不同,可选择的路径就会大不相同。如图1和图2所示,对于同一个赛场,两位选手的反应时间分别为2秒和1秒,而其到达终点所需的时间分别为18秒和16秒(赛车每秒可沿当前方向移动一格,从起点出发时算改变一次方向)。 由图1和图2可知,赛车的最短路线长度是由选手的反应灵敏度所决定的,当选手的反应很慢时,可能就不会存在可行的路径。你的任务是:在能够完成赛程(即存在从起点到终点的路径)的条件下,求出选手每个可能的反应时间所对应的最短路线长度。 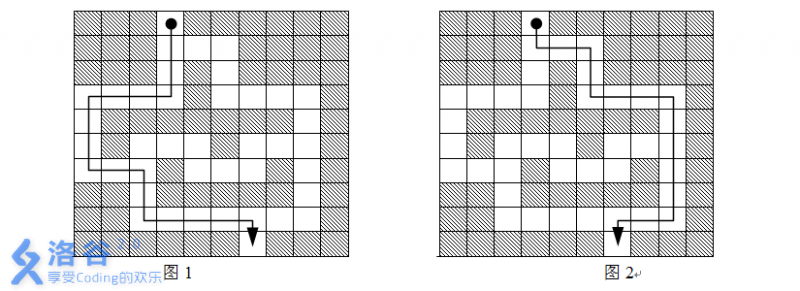
输入输出格式
输入格式
第一行包含两个整数N和M,表示赛场的长和宽。1≤N、M≤100。 第二行有四个整数x1、y1、x2、y2,表示赛程的起点和终点的位置分别为(x1,y1)和(x2,y2)。 接下来N行是一个N×M的01矩阵,矩阵中第i行第j列元素Aij=1表示赛场中位置(i,j)为赛道,Aij=0表示赛场中位置(i,j)有障碍物。
输出格式
输出文件可能有多行,其中每行输出一个可能的选手反应时间及该时间所对应的最短路线长度。输出文件中必须包含所有符合题目要求的选手反应时间。注意:由于选手的反应时间不可能很慢,因而不必考虑选手反应时间大于10秒的情况,只需输出10以内(包含10)的解。
输入输出样例
输入样例 #1
10 10
1 4 10 7
0 0 0 1 0 0 0 0 0 0
0 0 0 1 1 1 0 0 0 0
0 0 0 1 0 1 0 0 0 0
1 1 1 1 0 1 1 1 1 0
1 0 0 0 0 0 0 0 1 0
1 0 1 1 1 0 1 1 1 0
1 1 1 0 1 1 1 0 1 0
0 0 1 0 0 0 0 0 1 0
0 0 1 1 1 1 1 1 1 0
0 0 0 0 0 0 1 0 0 0
输出样例 #1
1 16
2 18
|
{
"url": "https://www.luogu.org/problem/P2226",
"source_domain": "www.luogu.org",
"snapshot_id": "crawl=CC-MAIN-2019-35",
"warc_metadata": {
"Content-Length": "12985",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:FXR7VO3I2OI7CRFWRHFADNLRYRATJE5A",
"WARC-Concurrent-To": "<urn:uuid:000a6a66-84d9-4e4d-85b6-d533dac7fc85>",
"WARC-Date": "2019-08-21T11:39:05Z",
"WARC-IP-Address": "47.246.18.233",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:5FOVAW5VZB2OSAAK75YIUKZQJCBVBYC5",
"WARC-Record-ID": "<urn:uuid:7ec929ce-5fbd-4cde-88e4-967502d0a8e5>",
"WARC-Target-URI": "https://www.luogu.org/problem/P2226",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:f415d149-6193-422e-8829-ea192240b35d>"
},
"warc_info": "isPartOf: CC-MAIN-2019-35\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for August 2019\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-109.ec2.internal\r\nsoftware: Apache Nutch 1.15 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.1-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
17,
18,
23,
24,
544,
545,
552,
553,
558,
559,
560,
718,
719,
724,
725,
726,
850,
851,
858,
859,
867,
868,
909,
951,
971,
991,
1011,
1031,
1051,
1071,
1091,
1111,
1131,
1151,
1152,
1160,
1161,
1166
],
"line_end_idx": [
17,
18,
23,
24,
544,
545,
552,
553,
558,
559,
560,
718,
719,
724,
725,
726,
850,
851,
858,
859,
867,
868,
909,
951,
971,
991,
1011,
1031,
1051,
1071,
1091,
1111,
1131,
1151,
1152,
1160,
1161,
1166,
1170
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 1170,
"ccnet_original_nlines": 38,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.01418440043926239,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.028368789702653885,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.8971630930900574,
"rps_doc_frac_unique_words": 0.19379845261573792,
"rps_doc_mean_word_length": 7.224806308746338,
"rps_doc_num_sentences": 5,
"rps_doc_symbol_to_word_ratio": 0.007092200219631195,
"rps_doc_unigram_entropy": 1.6391856670379639,
"rps_doc_word_count": 129,
"rps_doc_frac_chars_dupe_10grams": 0.05901287868618965,
"rps_doc_frac_chars_dupe_5grams": 0.10729613900184631,
"rps_doc_frac_chars_dupe_6grams": 0.10729613900184631,
"rps_doc_frac_chars_dupe_7grams": 0.10729613900184631,
"rps_doc_frac_chars_dupe_8grams": 0.09334763884544373,
"rps_doc_frac_chars_dupe_9grams": 0.08798283338546753,
"rps_doc_frac_chars_top_2gram": 0.08798283338546753,
"rps_doc_frac_chars_top_3gram": 0.09978540986776352,
"rps_doc_frac_chars_top_4gram": 0.09012875705957413,
"rps_doc_books_importance": -170.1534881591797,
"rps_doc_books_importance_length_correction": -170.1534881591797,
"rps_doc_openwebtext_importance": -86.52718353271484,
"rps_doc_openwebtext_importance_length_correction": -85.96699523925781,
"rps_doc_wikipedia_importance": -36.56034469604492,
"rps_doc_wikipedia_importance_length_correction": -36.56034469604492
},
"fasttext": {
"dclm": 0.09465097635984421,
"english": 0.00504670012742281,
"fineweb_edu_approx": 2.9613230228424072,
"eai_general_math": 0.8845446705818176,
"eai_open_web_math": 0.3393431305885315,
"eai_web_code": 0.8218113780021667
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "519.7",
"labels": {
"level_1": "Science and Natural history",
"level_2": "Mathematics",
"level_3": "Probabilities; or, Mathematical statistics"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "4",
"label": "Analyze"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "4",
"label": "Code/Software"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "4",
"label": "Missing Images or Figures"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "23",
"label": "Tutorial"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-5,651,461,206,135,818,000
|
Advertisement Upgrade to remove ads
What is the default configuration register value for a cisco router?
0x2102, which tells the router to load the IOS from flash memory as well as to load the configuration from NVRAM (startup-config).
What are the four step in the router boot sequence?
1. Power on self test (POST). The POST test the hardware to verify that all componets of the device are operational and present. The POST is stored in and run from ROM.
2. The bootstrap then looks for and loads the Cisco IOS software. Bootstarp is a program in rom. Cisco router looks for IOS by default in flash memory (EEPROM).
3. The IOS software looks for a valid configuration file store in NVRAM (startup-config).
4. If a startup-config is in NVRAM the router will copy the file and place it in RAM and call the file running-config. If a file is not found in NVRAM, the router will broadcast out any interface that detects carrier detect for a TFTP host looking for a configuration, and whe that fails it will start the setup mode configuration process.
What command shows you the current IOS image running?
show version
What is the frequency range of 802.11a standard?
5GHz
What is frequency range of 802.11b standard?
2.4GHz
What is the frequency range 802.11g standard?
2.4GHz
How man non-overlapping channels are available with 802.11a(h) standard?
23 non-overlapping channels.
How man non-overlapping channels are available with 802.11b standard?
3 non-overlapping channels.
How man non-overlapping channels are available with 802.11g standard?
3 non-overlapping channels.
What modulation technique does 802.11a (h) standard uses?
Orthogonal Frequency Division Multiplexing (OFDM) modulation.
What modulation technique does 802.11b standard uses?
Direct Sequence Spread Spectrum (DSSS) modulation.
What modulation technique does 802.11g standard uses?
Direct Sequence Spread Spectrum (DSSS) modulation. & Orthogonal Frequency Division Multiplexing (OFDM) modulation.
What is the significant change in 802.11n vs 802.11a/b/g?
802.11n build upon previous 802.11 standards by adding Multiple-Input Multiple-Output (MIMO), which employs multiple transmitters and receivers antennas to increase data throughput. 802.11n can have up to eight antennas.
What is the max data rate for the 802.11a standard?
54 Mbps
What is the max data rate for the 802.11b standard?
11 Mbps
What is the max data rate for the 802.11g standard?
54 Mbps
What is the maximum distance with maximum data rate for 802.11a?
The maximum data rate of up to 54 Mbps, but you need to be close to the access point, somewhere around 65 to 75 feet.
What is the maximum distance with maximum data rate for 802.11b?
The maximum data rate of up to 11 Mbps, and you can be around 150 feet, maybe farther, depending on condition.
What is the maximum distance with maximum data rate for 802.11g?
The maximum data rate of up to 54 Mbps, but you need to be close to the access point, somewhere around 90 to 100 feet.
What is the maximum distance running the lowest data rate for 802.11a?
lowest data rate is 6 Mbps, but it can run from a distnce of about 175 feet.
What is the maximum distance running the lowest data rate for 802.11b?
lowest data rate is 1 Mbps, but it can run from a distnce of about 350 feet.
What is the maximum distance running the lowest data rate for 802.11g?
lowest data rate is 6 Mbps, but it can run from a distnce of about 300 feet.
Cisco's Unified Wireless Solution provides a mesh solution. What device do you absolutely need to purchase to run a Cisco solution?
Controller and Access point
What is a Root Access Point (RAP)?
A access point connected to a wired network that serves as the gateway to the wired network. RAPs have a wired connection bact to a Cisco Wireless LAN Controller. They use the backhaul wireless interface to communicate with neighboring Mesh APs.
What is a Mesh Access Point (MAP)?
The Mesh APs are remote APs that are typically located on rooftops or towers and can connect up to 32 MAPs over a 5 GHz backhaul. During bootup, an access point will try to become a Root Access Point (RAP) if it's connected to the wired network. Conversely if a RAP loses its wired network connection, it will attempt to become a Mesh Access Point (MAP) and will serach for a RAP
What protocol is uses by Cisco Access point to determine the best path back to the wired network?
Adaptive Wireless Path Protocol (AWPP) - a protocol design by Cisco specifically for the wireless environment.
You are connection your access point and it is set to root. What does extended service set ID mean?
Extended service set ID means that you have more than one access point and they all are set to the same SSID and all are connected together in the same VLAN or distrubution system so users can roam.
What is the default serial encapsulation on Cisco routers?
High-Level Data-Link Control (HDLC)
What are the three PPP Data Link layer protocols?
Network Control Protocol (NCP), which defines the Network layer protocols; Link Control Protocol (LCP), a method of establishing, configuring, maintaining, and terminating the point-to-point connection; and High-Level Data-Link Control (HDLC), the MAC layer protocol that encapsulates the packets.
What is CIR in Frame Relay?
The Commited Information Rate (CIR) is the average rate, in bits per second, at which the Frame Relay switch agrees to transfer data.
What are the 3 encapsulation that CISCO supports on its serial interfaces?
HDLC, PPP, and Frame Relay.
Which command will display the CHAP authentication process as it occurs between two router in the network?
A. show chap authentication
B. show interface serial 0
C. debug ppp authentication
D. debug chap authentication
C. The command debug ppp authentication will show you the authentication proces that PPP uses between point-to-point connections.
Which Command is required for connectivity in a Frame Relay network if Inverse ARP is not operational?
A. frame relay arp
B. frame relay map
C. frame relay interface-dci
D. frame-relay lmi-type
B. If you have a router in your Frame Relay network thad does not support IARP, you must create Frame Relay maps on you router, which provide known DLCI-to-IP address mappings.
Suppose that you have a customer who has a central HQ and six branch offices. They anticipate adding six more brances in the near furture. They wish to implement a WAN technology that will allow the branches to economically connect to HQ and you have no free ports on the HQ router. Which of the following would you recommend?
A. PPP
B. HDLC
C. Frame Relay
D. ISDN
C. The key is "there are no free ports" on your router. Only Frame Relay can provide a connection to multiple locations with one interface, and in an economical manner no less.
Which of the following command options are displayed when you use the Router# show frame-relay command ? (Choose three.)
A. dlci
B. neighbors
C. lmi
D. pvc
E. map
C,D,E. The show frame-relay command provide may option, but the options available in the question are lmi, pvc, and map.
How should a router that is being used in a Frame Relay network be configured to keep split horizon issues from preventing routing updates?
A. Configure a separate subinterface for each PVC with a unique DLCI and subnet assigned to the subinterface.
B. Configure each Frame Relay circuit as a point-to-point line to support multicast and broadcast traffic.
C. Configure many subinterfaces in the same subnet.
D. Confiugre a single subinterface to establish multiple PVC connection to multiple remote router interfaces.
A. If you have a serial port confiured with multiple DLCIs connected to multiple remote sites, split horizon rules stop route updates received on an interface from being sent out the same interface. By creating subinterfaces for each PVC, you can avoid the split horizon issues when using Frame Relay.
Which encapsulation can be configured on a serial interface?
A. Ethernet
B. Token Ring
C. HDLC
D. Frame Relay
E. PPP
C, D, E. Ethernet and Token Ring are LAN techonologies and cannot be configured on a serial interface. PPP, HDLC, and Frame Relay are layer 2 WAN technologies that are typically confiugred on a serial interface.
When setting up Frame Relay for point-to-point subinterfaces, which of the following must not be configured?
A. The Frame Relay encapsulation on the physical interface
B. The local DLCI on each subinterface
C. An IP address on the physical interface
D. The subinterface type as point-to-point
C. It is very important to remember when studying the CCNA exam objectives, and when confiugring Frame Relay with point-to-point subinterfaces, that you do not put an IP address on the physical interface.
When a router is connected to a Frame Relay WAN link using a serail DTE interface, how is the clock rate determined?
A. Supplied by the CSU/DSU
B. By the far end router
C. By the clock rate command
D. By the physical layer bit stream timing
A. Clocking on a serial interface is always provided by the CSU/DSU (DCE device). However if you do not have a CSU/DSU in our nonproduction test environment, then you need to supply clocking with the clock rate command on the serial interface of the router with the DCE cable attached.
A default Frame Relay WAN is classified as what type of physical network?
A. Point-to-point
B. Broadcast multi-access
C. Non-broadcast multi-access
D. Non-broadcast multipoint
C. Frame Relay, by default, is a non-broadcast multi-access (NBMA) network, which means that broadcast, such as RIP updates, will not be forwarded across the link by default.
Which of the following encapsulates PPP frames in Ethernet frames and uses common PPP feautres like authentication, encryption, and compression?
A. PPP
B. PPoA
C. PPoE
D. TOken Ring
C. PPoE encapsulates PPP frames in Ethernet and uses common PPP features like authentication, encryption, and compression. PPPoA is used for ATM.
You need to configure a router for a Frame Relay connection to non-Cisco router. Which of the following commands will prepare the WAN interface of the router for this connection?
A. Router(config-if)#encapsulation frame-relay q933a
B. Router(config-if)#encapsulation frame-relay ansi
C. Router(config-if)#encapsulation frame-relay ietf
D. Router(config-if)#encapsulation frame-relay cisco
C. If you have a Cisco router on one side of a Frame Relay network and a non-Cisco router on the other side, you would need to use the Frame Relay encapsulation type of IETF. The default is Cisco encapsulation, which means that a Cisco router must be on both sides of the Frame Relay network.
The Acme Corporation is implementing dial-up services to enable remote-office employees to connect to the local network. The company uses multiple routed protocols, needs authentication of users connection to the network, and since some calls will be long distnace, needs call back support. Which of the following protocols is the best choice for these remote services?
A. 802.1
B. Frame Relay
C. HDLC
D. PPP
E. PAP
D. PPP is your only option, as HDLC and Frame Relay do not support these types of business requirements. PPP provides dynamic addressing, authentication using PAP or CHAP, and call-back services.
Which WAN encapsulations can be confiugred on an asynchronous serial connection? (Choose two.)
A. PPP
B. ATM
C. HDLC
D. SDLC
E. Frame Relay
A, B. Please do not freak out because ATM is an answer to this question. ATM is not covered in depth on the CCNA exam. PPP is mostly used for dial-up (async) services, but ATM could be used as well, though it typcially is not used anymore since PPP is so efficient.
Which of the following uses ATM as the Data Link layer protocol that's terminated at what's know as the DSLAM
A. DSL
B. PPPoE
C. Frame Relay
D. Dedicated T1
E. Wireless
F. POTS
A. ATM is the Data-Link layer protocol that's typically used over the DSL layer 1 connection from the CPE and terminated at what's known as the DSLAM 0 an ATM switch that contains DSL interface cards, or ATU-Cs.
Why won't the serial link between the Corp router the Remote router come up?
Corp#sh int s0/0
Serial0/0 is up, line protocol is down
Internet address is 10.0.1.1/24
Encapsulation PPP, loopback not set
Remote# sh int s0/0
Serial0/0 is up, line protocol is down
Internet address is 10.0.1.2/24
Encapsulation HDLC, loopback not set
A. The serial cable is faulty.
B. The IP addresses are not the same subnet.
C. The subnet mask are not correct.
D. The keepalive settings are not correct.
E. The layer 2 frames type are not compatible
E. This is an easy question because the Remote router is using the default HDLC serial encapsulation and the Corp router is using the PPP serail encapsulation. You should go to the Remote router and set that encapsulation to PPP or the Corp router back to the defualt HDLC.
In which of the following technologies is the term HFC used?
A. DSL
B. PPPoE
C. Frame Relay
D. Cable
E. Wireless
F. POTS
D. In a modern network, hybrid fiber-coaxial (HFC) is a telecommunication indusrtry term for a network that incorporates both optical fiber and coaxial cable to create a broadband network.
A remote site has just been connected to the cetral office. However, remote users cannot access applications at the central office. The remote router can be pinged from the central office router. Aftwer reviewing the command output shown below, which do you thing is the most likely reason for the problem?
Central# show running-config
interface Serial0
ip address 10.0.8.1 255.255.248.0
encapsulation frame-relay
frame-relay map ip 10.0.15.2 200
Router rip
Network 10.0.0.0
Remote# show running-config
interface Serial0
ip address 10.0.15.2 255.255.248.0
encapsulation frame-relay
frame-realy map ip 10.0.8.1 100
Router rip
Network 10.0.0.0
A. The Frame Relay PVC is down.
B. The IP addressing on the Central/Remote router link is incorrect.
C. Rip routing information is not being forwarded.
D. Frame Relay Inverse ARP is not properly configured.
C. Even though the IP addresses don't look correct, they are in the same subnet, so answer B is not correct. The question states that you can ping the other side, so the PVC must be up answer A can't be correct. You cannot configure IARP, so only answer C can be correct. Since a Frame Relay network is non0broadcast multi-access network by default, boradcast such as RIP updates cannot be sent across the PVC unless you use the broadcast statemetn at the end of the frame-relay map command.
Which of the following describes an industry-wide standsard suit of protocols and alogorithms that allows for secure data transmission over an IP-based network that function at the layer 3 Network layer of the OSI model?
A. HDLC
B. Cable
C. VPN
D. IPSec
E. xDSL
D. IPSec is and industry-wide standard suit of protocols and algorithms that allows for secure data transmission over an IP-based network taht funciotns at the layer 3 Network layer of the OSI model.
Which of the following describes the creation of private networks across the Internet, enabling privacy and tunneling of non-TCP/IP protocols?
A. HDLC
B. Cable
C. VPN
D. IPSec
E. xDSL
C. A VPN allows the creation of private networks across the Internet, enabling privacy and tunneling of non-TCP/IP protocols. A VPN can be set up across any type of link.
What function does the Frame Relay DLCI provide with respect to router A
Router A <--DLCI 100--> Flame Relay Switch <--DLCI 200-->Router B
A. Identifies the signaling standard between Router A and the frame switch
B. Identifies the circuit between RouterB and the frame switch
C. Identifies the encapsulation used between Router A and RouterB
D. Defines the signaling standard between RouterB and the frame switch.
A. DLCIs are locally significant only and define the circuit from the router to the switch only. They do not reference a remote router or DLCI. RouterA would use DLCI 100 to get to the RouterB network. Router B would use DLCI 200 to get to the Router A netwrok.
What is the command to see the encapsulation method on serial 0 of a Cisco router.
show interface serial 0
What are the commands to confiugre s0 to PPP encapsulation?
config t
int ser0
encapsulation ppp
What are the commands to configure a username of todd and password of cisco that is used on a Cisco router for PPP authenticaiton.
config t
username todd password cisco
What are the commands to enable CHAP authentication on a Cisco serial interface. (Assume PPP is the encapsulation type.)
config t
int s0
ppp authentication chap
What are the commands to configure the DLCI numbers for two serial interfaces, 0 and 1. Use 16 for s0 and 17 for s1.
config t
int s0
frame interface-dlci 16
int s1
frame interface-dlci 17
What are the commands to configure a remote office using a point-to-point subinterface. Use DLCI 16 and IP address 172.16.60.1/24
config t
int s0
encap frame
int s0.16 point-to-point
ip address 172.16.60.1 255.255.255.0
frame interface-dlci 16
What protocol would you use if you were running xDSL and needed authentication?
PPPoE
What are the three protocols specified in PPP?
HDLC, LCP and NCP
To provide security in your VPN tunnel, what protocol suite would you use?
IPsec
What are the typical three different categories of VPNs?
Remote access VPNs, site-to-site VPNs, and extranet VPNs
Which of the following is true when describing a global unicast address?
A. Packets addressed to a unicast address are delivered to a single interface.
B. These are your typical publicly routable addresses, just like a regular publicly routable address in IPv4.
C. These are like private addresses in IPv4 in that they are not meant to be routed.
D. These addresses are meant for nonrouting purposes, but they are almost globally unique so it is unlikely the will have an address overlap.
B. Unlike unicast addresses, global unicast addresses are meant to be routed.
Which of the following is true when describing a unicast address?
A. Packets addressed to a unicast address are delivered to a single interface.
B. These are your typical publicly routable addresses, just like a regular publicly routable address in IPv4.
C. These are like private addresses in IPv4 in that they are not meant to be routed.
D. These addresses are meant for nonrouting purposes, but they are almost globally unique so it is unlikely the will have an address overlap.
A. Packets addressed to a unicast address are delivered to a single interface. For load balancing, multiple interface can use the same address.
Which of the following is true when describing a link-local address?
A. Packets addressed to a unicast address are delivered to a single interface.
B. These are your typical publicly routable addresses, just like a regular publicly routable address in IPv4
C. These are like private addresses in IPv44 in that they are not meant to be routed.
D. These addresses are meant for nonrouting purposes, but they are almost globablly unique so it is unlikely they will have an address overlap.
C. Link-local address are meant for throwing together a temporary LAN for meetings or a local small LAN that is not going to be routed but needs to share and access files and services locally.
Which of the following is true when describing a unique local address?
A. Packets addressed to a unicast address are delivered to a single interface.
B. These are your typical publicly routable addresses, just like a regular publicly routable address in IPv4
C. These are like private addreses in IPv4 in that they are not meant to be routed.
D. These addresses are meant for nonrouting purpose, but they are almost globally unique so it is unlikely they will have an address overlap.
D. These addresses are meant for nonrouting purposes like link-local, but they are almost globally unique so it is unlikely they will have an address overlap. Unique local addresses were designed as a replacement for sire-local addresses.
Which of the following is true when describing a multicast address?
A. Packets addressed to a unicast address are delivered to a single interface.
B. Packets are delivered to all interfaces identified by the address. Thi is also called a one-to-many address.
C. Identifies multiple interfaces and is only delivered to one address. This address can also be called one-to-one-of-many.
D. These addresses are meant for nonrouting purpose, but they are almost globally unique so it is unlikely they will have an address overlap.
B. Packets addressed to a multicast address are delivered to all interfaces identified by the multicast address, the same as in IPv4. It is also called a one-to-many address. You can always tell a multicast address in IPv6 because multicast addresses always start with FF
Which of the following is ture when describing an anycast address?
A. Packets addressed to a unicast address are delivered to a single interface.
B. Packets are delivered to all interfaces identified by the address. Thi is also called a one-to-many address.
C. This address identifies multiple interfaces and the anycast acket is only delivered to one address. This address can also be called one-to-one-of-many
D. These addresses are meant for nonrouting purpose, but they are almost globally unique so it is unlikely they will have an address overlap.
C. Anycast addresses identify multiple interfaces, which is the same as multicast; however, the big difference is that the anycast packet is only delivered to one address, the first one it finds defined in the terms of routing distance. This address can also be called one-to-one-of-many.
You want to pin the loopback address of your local host. What will you type?
A. ping 127.0.0.1
B. ping 0.0.0.0
C. ping ::1
D. trace 0.0.::1
C. The loopback address with IPv4 is 127.0.0.1. With IPv6, that address is ::1.
What two multicast addresses does OSPFv3 use?
A. FF02::A
B. FF02::9
C. FF02::5
D. FF02::6
C, D. Adjacencies and next-hop attributes now use lonk-local addresses, and OSPFv3 still uses multicast traffic to send its updates and acknowedgments with the addresses FF02::5 for OSPF routers and FF0::6 for OSPF designated routers. These are the replacements for 224.0.0.5 and 224.0.0.6, respectively.
What multicast addresses does RIPng use?
A. FF02::A
B. FF02::9
C. FF02::5
D. FF02::6
B. RIPng uses the multicast IPV6 address of FF02::9. If you remember the multicast addresses for IPV4, the numbers at the end of each IPv6 address are the same.
What multicast addresses does EIGRPv6 use?
A. FF02::A
B. FF02::9
C. FF02::5
D. FF02::6
A. EIGRPv6's multicast address stayed very near the same. In IPv4 it was 224.0.0.10; now it is FF02::A
To enable RIPng, which of the following would you use?
A. Router1(config-if)#ipv6 ospf 10 area 0.0.0.0
B. Router1(config-if)#ipv6 rip 1 enable
C. Router1(config-if)#ipv6 router eigrp 10
D. Router1(config-rtr)#no shutdown
E. Router1(config-if)#ipv6 eigrp 10
B. It's pretty simple to enable RIPng for IPv6. You configure it right on the interface where you want RIP to run with the ipv6 router rip number command.
To enable EiGRP, which three of the following would you use?
A. Router1(config-if)#ipv6 ospf 10 area 0.0.0.0
B. Router1(config-if)#ipv6 router rip 1
C. Router1(config-if)#ipv6 router eigrp 10
D. Router1(config-rtr)#no shutdown
E. Router1(config-if)#ipv6 eigrp 10
C, D, E. Unlike RIPng and OSPFv3, you need to configure EIGRP both from global configuration mode and from interface mode, and you have to enable the command with the no shutdown command.
To enable OSPFv3, which of the following would you use?
A. Router1(config-if)#ipv6 ospf 10 area 0.0.0.0
B. Router1(config-if)#ipv6 router rip 1
C. Router1(config-if)#ipv6 router eigrp 10
D. Router1(config-rtr)#no shutdown
E. Router1(config-if)#ospf ipv6 10 area 0
A. To enable OSPFv3, you enable the protocol as with RIPng, The command string is ipv6 ospf prcess-id area area-id
What two statements about IPv6 address are true? (Choose two.)
A. Leading zeros are required
B. Two colons (::) are used to represent successive hexademical fields of zeros.
C. Tow collons (::) are used to separate fields.
D. A single interface will have multiple IPv6 addresses of different types.
B, D. In order to shorten the written length of an IPv6 address, successive fields of zero may be replace by double colons. In trying to shorten the address further, leading zeros may also be removed. Just as with IPv4, a single device's interface can have more than one address; with IPv6 there are more types of addresses and the same rule applies. There can be link-local, global unicast, and multicast addresses all assigned to the same interface.
What two statements about IPv4 and IPv6 addresses are true?
A. An IPv6 address is 32 bit long, represented in hexidecimal.
B. An IPv6 address is 128 bit long, represented in decimal.
C.An IPv4 address is 32 bit long, represented in decimal
D. An IPv6 address is 128 bits long, represented in hexidecimal.
C, D. IPv4 address are 32 bits long and are represented in decimal format. IPv6 addresses are 128 bits long and represented in hexadecimal format.
Which type of packet is addressed and delivered to only a single interface?
Unicast
Which type of address is used just like a regular public routable addrss in IPv4?
Global unicast
Which type of address is not meant to be routed?
Link-local
Which type of address is not meant to be routed to the Internet but is still globally unique?
Unique local (used to be called site-local)
Which type of address is meant to be delivered to multiple interfaces?
Multicast
Which type of address identifies multiple interfaces, but packets are delivered only to the first address it finds.?
Anycast
Which routing protocol uses multicast address FF02::5?
OSPF
IPv4 had a loopback address of 127.0.0.1 . What is the IPv6 loopback address?
::1
What does a link-local address always start with?
FE80::
What does a unque local unicast range start with?
FC00::
In IPv6 What is the global unicast address range?
2000::/3
In IPv6 what is the unique local unicast range.
FC00::/7
In IPv6 what is the link-local unicast range?
FF80::/10
In IPv6 what is the multicast range?
FF00::/8
In IPv6 what is the resereved ip range for examples and documentation?
3FFF::FFFF::/32
2001:0DB8::/32
Inn IPv6 what ip rage is used with 6to4; the structure that allows IPv6 packets to be transmitted over an IPv4 network without the need to configure explicit tunnels.
2002::/16
What type of address translation can use only one address to allow thoussands of hosts to be translated globally?
Port Address Translation (PAT), also called NAT Overload.
What commnad can you use to show the NAT translation as the occur on your router?
debug ip nat.
What command will show you the translation table?
show ip nat translations.
How much memory does each NAT mapping use (approximately)?
160 bytes of memory.
Why would you use the ip nat translation max-entries command?
In the rare case where the entries must be limited for either performance or policy reasons.
Which command can be used for troubleshooting and displays a summary of the NAT configuration as well as count of active translation types and hits to an existing mapping.
show ip nat statistics.
What commands must be used on your router interfaces before NAT will translate addresses?
The ip nat inside and ip nat outside commands
In the following output, what type of NAT is being used?
ip nat pool todd-nat 170.168.10.10 170.168.10.20 netmask 255.255.255.0
Dynamic NAT
Instead of the netmask command, you can use the _______ statement.
prefix-length
What command will clear all your NAT entries from the translation table?
clear ip nat translations *
Which of the following are disadvantages of using NAT? (Choose three.)
A. Translation introduces switching path delays.
B. Conserves legally registered addresses.
C. Causes loss of end-to-end IP traceability.
D. Increases flexibility when connecting to the Internet.
E. Certain applications will not function with NAT enabled.
F. Reduces address overlap occurrence.
A, C, E. NAT is not perfect and cause some issues in some networks, but most networks work just fine. NAT can cause delays and troubleshooting problems, and some applications just won't work.
Which of the following are advantages of using NAT? (Choose three.)
A. Translation introduces switching path delays.
B. Conserves legally registered addresses.
C. Causes loss of end-to-end IP traceability.
D. Increases flexibility when connecting to the Internet.
E. Certain applications will not function with NAT enabled.
F. Reduces address overlap occurrence.
B, D, F. NAT is not perfect, but there are some advantages. It conserves global addresses, which allow us to add millions of hosts to the Internet without "real" IP addresses. This provides flexibility in our corporate networks. NAT can also allow you to use the same subnet more than once in the same network without overlapping networks.
Which command will allow you to see real-time translation on your router?
A. show ip nat translations
B. show ip nat statistics
C. debug ip nat
D. clear ip nat translations *
C. The command debug ip nat will show you in real time the translation occurring on your router.
Which command will clear all the translation active on your router?
A. show ip nat translations
B. show ip nat statistics
C. debug ip nat
D. clear ip nat translations *
D. the command clear ip nat translation * will clear all the active NAT entries in your translation table.
Which command will show you the summary of the NAT configurations?
A. show ip nat translations
B. show ip nat statistics
C. debug ip nat
D. clear ip nat trnslations *
B. The show ip nat statistics command displays a summary of the NAT configuration as well as counts of active translation types, hits to an existing mapping, misses (causing an attempt to create a mapping), and expired translations.
Which command will create a dynamic pool name Todd that will provide you with 30 global addrsses?
A. ip nat pool Todd 171.16.10.65 171.16.10.94 net 255.255.2255.240
B. ip nat pool Todd 171.16.10.65 171.16.10.94 net 255.255.255.224
C. ip nat pool todd 171.16.10.65 171.16.10.94 net 255.255.255.224
D. ip nat pool Todd 171.16.10.1 171.16.10.254 net 255.255.255.0
B. The command ip nat pool name createes the pool that hosts can use to get onto the global Internet. What makes answer B correct is that the range 171.16.10.65 through 171.16.10.94 includes 30 hosts, but the mask has to match 30 hosts as well, and that mask is 255.255.255.224. Answer C is wrong becuase the pool name has a lower case "T" in the pool name. Pool name's are case sensitive.
Which are considered the three methods of NAT?
A. Static
B. IP NAT pool
C. Dynamic
D. Nat double-translation
E. Overload
A, C, E. YOu can configure NAT three ways on a Cisco router: static, dynamic, and NAT Overload (PAT).
When creating a pool of global addrsses, which of the following can be used instead of the netmask command?
A. / (slash notiation)
B. prefix-length
C. no mask
D. block-size
B. Instead of the netmask command, you can use the "prefix-length length" statement.
Which of the following would be a good starting point for troubleshooting if your router is not translating?
A. Reboot.
B. Call Cisco.
C. Check your interfaces for the correct configuration.
D. Run the debug all command.
C. IN order for NAT to provide translation services, you must have ip nat inside and ip nat outside configured on your router's interfaces.
Which o fthe following would be good reasons to run NAT? (Choose three.)
A. you need to connect to the Internet and your hosts don't have globally unique IP addresses.
B. You change to a new ISP that requires you to renumber your network.
C. You don't want any host connecting to the Internet.
D. You requrie two intranets with duplicate addresses to merge.
A, B, D. The most popular use of NAT is if you want to connect to the Internect and you don't want hosts to have global (real) IP addresses, but answeres B and D are correct as well.
Which of the following is considered to be the address after translation?
A. Inside local
B. Outside local
C. Inside global
D. Outside global
C. The host on the private network after translation is considered to be an inside global host.
Which of the following is considered to be the address before translation?
A. Inside local
B. Outside local
C. Inside global
D. Outside global
A. The host on the privae network before translation is considered to be an inside local host.
Which of the following is considered to be the destination host before translation?
A. Inside local
B. Outside local
C. Inside global
D. Outside global
B. The host on the global network before translation is considered to be an outsid local host
Which of the following is considered to be the outside destination host after translation?
A. Inside local
B. Outside local
C. Inside global
D. Outside global
D. The host on the global network after translation is considred to be an outside global host.
Which command would you place on interface on a private network?
A. ip nat inside
B. ip nat outside
C. ip outside global
D. ip inside local
A. As in access-lists, you must configure your interfaces before NAT will provide any translations. On the inside networks you would use the command ip nat inside. On the outside interface, you will use the command ip nat outside.
Which command would you place on interface connected to the Internet?
A. ip nat inside
B. ip nat outside
C. ip outside global
D. ip inside local
B. As in access-lists, you must configure your interfaces before NAT will provide any translations. On the inside networks you would use the command ip nat inside. On the outside interface, you will use the command ip nat outside.
Pat addressTranslation is also termed what?
A. NAT Fast
B. NAT Static
C. NAT Overloading Static
D. Overloading Static
C. Another term for port address translation is NAT Overload because that is the command used to enable port address translation.
Which command will show you all the translation active on your router?
A. show ip nat translations
B. show ip nat statistics
C. debug ip nat
D. clear ip nat translations *
A. The show ip nat translation will show you the translation table containing all the active NAT entries.
Which of the following is an example of standard IP access list?
A. access-list 110 permit host 1.1.1.1
B. access-list 1 deny 172.16.10.1 0.0.0.0
C. access-list 1 permit 172.16.10.1 255.255.0.0
D. access-list standard 1.1.1.1
B. Standard Ip access list use the number 1-99 and 1300-1999 and filter based on source IP address only. Option C is incorrect because the mask must be in wildcard format.
You need to create an access list that will prevent hosts in the network range of 192.168.160.0 to 192.168.191.0. Which of the following lists will you use?
A. access-llist 10 deny 192.168.160.0 255.255.224.0
B. access-llist 10 deny 192.168.160.0 0.0.191.255
C. access-list 10 deny 192.168.160.0 0.0.31.255
D. access-list 10 deny 192.168.0.0 0.0.31.255
C. The range of 192.168.160.0 to 192.168.191.0 is a block size of 32. The network address is 192.168.160.0 and the mask would be 255.255.224.0, which for an access list must be wildcard format of 0.0.32.255. The 31 is used for a block size of 32. The wildccard is always one less than the block size.
Please allow access to your computer’s microphone to use Voice Recording.
Having trouble? Click here for help.
We can’t access your microphone!
Click the icon above to update your browser permissions above and try again
Example:
Reload the page to try again!
Reload
Press Cmd-0 to reset your zoom
Press Ctrl-0 to reset your zoom
It looks like your browser might be zoomed in or out. Your browser needs to be zoomed to a normal size to record audio.
Please upgrade Flash or install Chrome
to use Voice Recording.
For more help, see our troubleshooting page.
Your microphone is muted
For help fixing this issue, see this FAQ.
Star this term
You can study starred terms together
NEW! Voice Recording
Create Set
|
{
"url": "http://quizlet.com/2724558/cisco-flash-cards/",
"source_domain": "quizlet.com",
"snapshot_id": "crawl=CC-MAIN-2014-35",
"warc_metadata": {
"Content-Length": "263733",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:6UGBH4GBNNYZ75P3NIAS4ZOCXSMKWF4A",
"WARC-Concurrent-To": "<urn:uuid:6fea3620-d311-4d92-a552-51ce679b225d>",
"WARC-Date": "2014-08-20T22:35:54Z",
"WARC-IP-Address": "104.16.20.190",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:6YG4QQBEJOZKCQOA4VIATYTC3AJLMAIZ",
"WARC-Record-ID": "<urn:uuid:da5c72c0-17b6-4263-ab01-74603411b8ba>",
"WARC-Target-URI": "http://quizlet.com/2724558/cisco-flash-cards/",
"WARC-Truncated": "length",
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:cb029bb0-60aa-41ce-932e-9d837563f340>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-180-136-8.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2014-35\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web with URLs provided by Blekko for August 2014\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
36,
37,
106,
107,
238,
239,
291,
292,
461,
622,
712,
1052,
1053,
1107,
1108,
1121,
1122,
1171,
1172,
1177,
1178,
1223,
1224,
1231,
1232,
1278,
1279,
1286,
1287,
1360,
1361,
1390,
1391,
1461,
1462,
1490,
1491,
1561,
1562,
1590,
1591,
1649,
1650,
1712,
1713,
1767,
1768,
1819,
1820,
1874,
1875,
1990,
1991,
2049,
2050,
2271,
2272,
2324,
2325,
2333,
2334,
2386,
2387,
2395,
2396,
2448,
2449,
2457,
2458,
2523,
2524,
2642,
2643,
2708,
2709,
2820,
2821,
2886,
2887,
3006,
3007,
3078,
3079,
3156,
3157,
3228,
3229,
3306,
3307,
3378,
3379,
3456,
3457,
3589,
3590,
3618,
3619,
3654,
3655,
3901,
3902,
3937,
3938,
4318,
4319,
4417,
4418,
4529,
4530,
4630,
4631,
4830,
4831,
4890,
4891,
4927,
4928,
4978,
4979,
5277,
5278,
5306,
5307,
5441,
5442,
5517,
5518,
5546,
5547,
5654,
5655,
5683,
5710,
5738,
5767,
5768,
5898,
5899,
6002,
6003,
6022,
6041,
6070,
6094,
6095,
6272,
6273,
6600,
6601,
6608,
6616,
6631,
6639,
6640,
6817,
6818,
6939,
6940,
6948,
6961,
6968,
6975,
6982,
6983,
7104,
7105,
7245,
7246,
7356,
7463,
7515,
7625,
7626,
7928,
7929,
7990,
7991,
8003,
8017,
8025,
8040,
8047,
8048,
8260,
8261,
8370,
8371,
8430,
8469,
8512,
8555,
8556,
8761,
8762,
8879,
8880,
8907,
8932,
8961,
9004,
9005,
9291,
9292,
9366,
9367,
9385,
9411,
9441,
9469,
9470,
9645,
9646,
9791,
9792,
9799,
9807,
9815,
9829,
9830,
9976,
9977,
10156,
10157,
10210,
10262,
10314,
10367,
10368,
10661,
10662,
11032,
11033,
11042,
11057,
11065,
11072,
11079,
11080,
11276,
11277,
11372,
11373,
11380,
11387,
11395,
11403,
11418,
11419,
11685,
11686,
11796,
11797,
11804,
11813,
11828,
11844,
11856,
11864,
11865,
12077,
12078,
12155,
12156,
12173,
12212,
12244,
12280,
12281,
12301,
12340,
12372,
12409,
12410,
12441,
12486,
12522,
12565,
12611,
12612,
12886,
12887,
12948,
12949,
12956,
12965,
12980,
12989,
13001,
13009,
13010,
13199,
13200,
13507,
13508,
13537,
13555,
13589,
13615,
13648,
13659,
13676,
13677,
13705,
13723,
13758,
13784,
13816,
13827,
13844,
13845,
13877,
13946,
13997,
14052,
14053,
14545,
14546,
14767,
14768,
14776,
14785,
14792,
14801,
14809,
14810,
15010,
15011,
15154,
15155,
15163,
15172,
15179,
15188,
15196,
15197,
15368,
15369,
15442,
15443,
15509,
15510,
15585,
15648,
15714,
15786,
15787,
16049,
16050,
16133,
16134,
16158,
16159,
16219,
16220,
16229,
16238,
16256,
16257,
16388,
16389,
16398,
16427,
16428,
16549,
16550,
16559,
16566,
16590,
16591,
16708,
16709,
16718,
16725,
16749,
16756,
16780,
16781,
16911,
16912,
16921,
16928,
16940,
16965,
17002,
17026,
17027,
17107,
17108,
17114,
17115,
17162,
17163,
17181,
17182,
17257,
17258,
17264,
17265,
17322,
17323,
17380,
17381,
17454,
17455,
17534,
17644,
17729,
17871,
17872,
17950,
17951,
18017,
18018,
18097,
18207,
18292,
18434,
18435,
18579,
18580,
18649,
18650,
18729,
18838,
18924,
19068,
19069,
19262,
19263,
19334,
19335,
19414,
19523,
19607,
19749,
19750,
19989,
19990,
20058,
20059,
20138,
20250,
20374,
20516,
20517,
20789,
20790,
20857,
20858,
20937,
21049,
21203,
21345,
21346,
21635,
21636,
21713,
21714,
21732,
21748,
21760,
21777,
21778,
21858,
21859,
21905,
21906,
21917,
21928,
21939,
21950,
21951,
22256,
22257,
22298,
22299,
22310,
22321,
22332,
22343,
22344,
22505,
22506,
22549,
22550,
22561,
22572,
22583,
22594,
22595,
22698,
22699,
22754,
22755,
22803,
22843,
22886,
22921,
22957,
22958,
23113,
23114,
23175,
23176,
23224,
23264,
23307,
23342,
23378,
23379,
23567,
23568,
23624,
23625,
23673,
23713,
23756,
23791,
23833,
23834,
23949,
23950,
24013,
24014,
24044,
24125,
24174,
24250,
24251,
24703,
24704,
24764,
24765,
24828,
24888,
24945,
25010,
25011,
25158,
25159,
25235,
25236,
25244,
25245,
25327,
25328,
25343,
25344,
25393,
25394,
25405,
25406,
25500,
25501,
25545,
25546,
25617,
25618,
25628,
25629,
25746,
25747,
25755,
25756,
25811,
25812,
25817,
25818,
25896,
25897,
25901,
25902,
25952,
25953,
25960,
25961,
26011,
26012,
26019,
26020,
26070,
26071,
26080,
26081,
26129,
26130,
26139,
26140,
26186,
26187,
26197,
26198,
26235,
26236,
26245,
26246,
26317,
26318,
26334,
26349,
26350,
26517,
26518,
26528,
26529,
26643,
26644,
26702,
26703,
26785,
26786,
26800,
26801,
26851,
26852,
26878,
26879,
26938,
26939,
26960,
26961,
27023,
27024,
27117,
27118,
27290,
27291,
27315,
27316,
27406,
27407,
27453,
27454,
27511,
27512,
27583,
27584,
27596,
27597,
27664,
27665,
27679,
27680,
27753,
27754,
27782,
27783,
27854,
27855,
27904,
27947,
27993,
28051,
28111,
28150,
28151,
28343,
28344,
28412,
28413,
28462,
28505,
28551,
28609,
28669,
28708,
28709,
29049,
29050,
29124,
29125,
29153,
29179,
29195,
29226,
29227,
29324,
29325,
29393,
29394,
29422,
29448,
29464,
29495,
29496,
29603,
29604,
29671,
29672,
29700,
29726,
29742,
29772,
29773,
30006,
30007,
30105,
30106,
30173,
30239,
30305,
30369,
30370,
30760,
30761,
30808,
30809,
30819,
30834,
30845,
30871,
30883,
30884,
30986,
30987,
31095,
31096,
31119,
31136,
31147,
31161,
31162,
31247,
31248,
31357,
31358,
31369,
31384,
31440,
31470,
31471,
31611,
31612,
31685,
31686,
31781,
31852,
31907,
31971,
31972,
32155,
32156,
32230,
32231,
32247,
32264,
32281,
32299,
32300,
32396,
32397,
32472,
32473,
32489,
32506,
32523,
32541,
32542,
32637,
32638,
32722,
32723,
32739,
32756,
32773,
32791,
32792,
32886,
32887,
32978,
32979,
32995,
33012,
33029,
33047,
33048,
33143,
33144,
33209,
33210,
33227,
33245,
33266,
33285,
33286,
33517,
33518,
33588,
33589,
33606,
33624,
33645,
33664,
33665,
33896,
33897,
33941,
33942,
33954,
33968,
33994,
34016,
34017,
34147,
34148,
34219,
34220,
34248,
34274,
34290,
34321,
34322,
34428,
34429,
34494,
34495,
34534,
34576,
34624,
34656,
34657,
34829,
34830,
34987,
34988,
35040,
35090,
35138,
35184,
35185,
35486,
35487,
35561,
35562,
35599,
35600,
35633,
35634,
35710,
35711,
35720,
35721,
35751,
35752,
35759,
35760,
35791,
35792,
35824,
35825,
35945,
35946,
35985,
36009,
36010,
36055,
36056,
36081,
36082,
36124,
36125,
36140,
36141,
36178,
36179,
36200,
36201
],
"line_end_idx": [
36,
37,
106,
107,
238,
239,
291,
292,
461,
622,
712,
1052,
1053,
1107,
1108,
1121,
1122,
1171,
1172,
1177,
1178,
1223,
1224,
1231,
1232,
1278,
1279,
1286,
1287,
1360,
1361,
1390,
1391,
1461,
1462,
1490,
1491,
1561,
1562,
1590,
1591,
1649,
1650,
1712,
1713,
1767,
1768,
1819,
1820,
1874,
1875,
1990,
1991,
2049,
2050,
2271,
2272,
2324,
2325,
2333,
2334,
2386,
2387,
2395,
2396,
2448,
2449,
2457,
2458,
2523,
2524,
2642,
2643,
2708,
2709,
2820,
2821,
2886,
2887,
3006,
3007,
3078,
3079,
3156,
3157,
3228,
3229,
3306,
3307,
3378,
3379,
3456,
3457,
3589,
3590,
3618,
3619,
3654,
3655,
3901,
3902,
3937,
3938,
4318,
4319,
4417,
4418,
4529,
4530,
4630,
4631,
4830,
4831,
4890,
4891,
4927,
4928,
4978,
4979,
5277,
5278,
5306,
5307,
5441,
5442,
5517,
5518,
5546,
5547,
5654,
5655,
5683,
5710,
5738,
5767,
5768,
5898,
5899,
6002,
6003,
6022,
6041,
6070,
6094,
6095,
6272,
6273,
6600,
6601,
6608,
6616,
6631,
6639,
6640,
6817,
6818,
6939,
6940,
6948,
6961,
6968,
6975,
6982,
6983,
7104,
7105,
7245,
7246,
7356,
7463,
7515,
7625,
7626,
7928,
7929,
7990,
7991,
8003,
8017,
8025,
8040,
8047,
8048,
8260,
8261,
8370,
8371,
8430,
8469,
8512,
8555,
8556,
8761,
8762,
8879,
8880,
8907,
8932,
8961,
9004,
9005,
9291,
9292,
9366,
9367,
9385,
9411,
9441,
9469,
9470,
9645,
9646,
9791,
9792,
9799,
9807,
9815,
9829,
9830,
9976,
9977,
10156,
10157,
10210,
10262,
10314,
10367,
10368,
10661,
10662,
11032,
11033,
11042,
11057,
11065,
11072,
11079,
11080,
11276,
11277,
11372,
11373,
11380,
11387,
11395,
11403,
11418,
11419,
11685,
11686,
11796,
11797,
11804,
11813,
11828,
11844,
11856,
11864,
11865,
12077,
12078,
12155,
12156,
12173,
12212,
12244,
12280,
12281,
12301,
12340,
12372,
12409,
12410,
12441,
12486,
12522,
12565,
12611,
12612,
12886,
12887,
12948,
12949,
12956,
12965,
12980,
12989,
13001,
13009,
13010,
13199,
13200,
13507,
13508,
13537,
13555,
13589,
13615,
13648,
13659,
13676,
13677,
13705,
13723,
13758,
13784,
13816,
13827,
13844,
13845,
13877,
13946,
13997,
14052,
14053,
14545,
14546,
14767,
14768,
14776,
14785,
14792,
14801,
14809,
14810,
15010,
15011,
15154,
15155,
15163,
15172,
15179,
15188,
15196,
15197,
15368,
15369,
15442,
15443,
15509,
15510,
15585,
15648,
15714,
15786,
15787,
16049,
16050,
16133,
16134,
16158,
16159,
16219,
16220,
16229,
16238,
16256,
16257,
16388,
16389,
16398,
16427,
16428,
16549,
16550,
16559,
16566,
16590,
16591,
16708,
16709,
16718,
16725,
16749,
16756,
16780,
16781,
16911,
16912,
16921,
16928,
16940,
16965,
17002,
17026,
17027,
17107,
17108,
17114,
17115,
17162,
17163,
17181,
17182,
17257,
17258,
17264,
17265,
17322,
17323,
17380,
17381,
17454,
17455,
17534,
17644,
17729,
17871,
17872,
17950,
17951,
18017,
18018,
18097,
18207,
18292,
18434,
18435,
18579,
18580,
18649,
18650,
18729,
18838,
18924,
19068,
19069,
19262,
19263,
19334,
19335,
19414,
19523,
19607,
19749,
19750,
19989,
19990,
20058,
20059,
20138,
20250,
20374,
20516,
20517,
20789,
20790,
20857,
20858,
20937,
21049,
21203,
21345,
21346,
21635,
21636,
21713,
21714,
21732,
21748,
21760,
21777,
21778,
21858,
21859,
21905,
21906,
21917,
21928,
21939,
21950,
21951,
22256,
22257,
22298,
22299,
22310,
22321,
22332,
22343,
22344,
22505,
22506,
22549,
22550,
22561,
22572,
22583,
22594,
22595,
22698,
22699,
22754,
22755,
22803,
22843,
22886,
22921,
22957,
22958,
23113,
23114,
23175,
23176,
23224,
23264,
23307,
23342,
23378,
23379,
23567,
23568,
23624,
23625,
23673,
23713,
23756,
23791,
23833,
23834,
23949,
23950,
24013,
24014,
24044,
24125,
24174,
24250,
24251,
24703,
24704,
24764,
24765,
24828,
24888,
24945,
25010,
25011,
25158,
25159,
25235,
25236,
25244,
25245,
25327,
25328,
25343,
25344,
25393,
25394,
25405,
25406,
25500,
25501,
25545,
25546,
25617,
25618,
25628,
25629,
25746,
25747,
25755,
25756,
25811,
25812,
25817,
25818,
25896,
25897,
25901,
25902,
25952,
25953,
25960,
25961,
26011,
26012,
26019,
26020,
26070,
26071,
26080,
26081,
26129,
26130,
26139,
26140,
26186,
26187,
26197,
26198,
26235,
26236,
26245,
26246,
26317,
26318,
26334,
26349,
26350,
26517,
26518,
26528,
26529,
26643,
26644,
26702,
26703,
26785,
26786,
26800,
26801,
26851,
26852,
26878,
26879,
26938,
26939,
26960,
26961,
27023,
27024,
27117,
27118,
27290,
27291,
27315,
27316,
27406,
27407,
27453,
27454,
27511,
27512,
27583,
27584,
27596,
27597,
27664,
27665,
27679,
27680,
27753,
27754,
27782,
27783,
27854,
27855,
27904,
27947,
27993,
28051,
28111,
28150,
28151,
28343,
28344,
28412,
28413,
28462,
28505,
28551,
28609,
28669,
28708,
28709,
29049,
29050,
29124,
29125,
29153,
29179,
29195,
29226,
29227,
29324,
29325,
29393,
29394,
29422,
29448,
29464,
29495,
29496,
29603,
29604,
29671,
29672,
29700,
29726,
29742,
29772,
29773,
30006,
30007,
30105,
30106,
30173,
30239,
30305,
30369,
30370,
30760,
30761,
30808,
30809,
30819,
30834,
30845,
30871,
30883,
30884,
30986,
30987,
31095,
31096,
31119,
31136,
31147,
31161,
31162,
31247,
31248,
31357,
31358,
31369,
31384,
31440,
31470,
31471,
31611,
31612,
31685,
31686,
31781,
31852,
31907,
31971,
31972,
32155,
32156,
32230,
32231,
32247,
32264,
32281,
32299,
32300,
32396,
32397,
32472,
32473,
32489,
32506,
32523,
32541,
32542,
32637,
32638,
32722,
32723,
32739,
32756,
32773,
32791,
32792,
32886,
32887,
32978,
32979,
32995,
33012,
33029,
33047,
33048,
33143,
33144,
33209,
33210,
33227,
33245,
33266,
33285,
33286,
33517,
33518,
33588,
33589,
33606,
33624,
33645,
33664,
33665,
33896,
33897,
33941,
33942,
33954,
33968,
33994,
34016,
34017,
34147,
34148,
34219,
34220,
34248,
34274,
34290,
34321,
34322,
34428,
34429,
34494,
34495,
34534,
34576,
34624,
34656,
34657,
34829,
34830,
34987,
34988,
35040,
35090,
35138,
35184,
35185,
35486,
35487,
35561,
35562,
35599,
35600,
35633,
35634,
35710,
35711,
35720,
35721,
35751,
35752,
35759,
35760,
35791,
35792,
35824,
35825,
35945,
35946,
35985,
36009,
36010,
36055,
36056,
36081,
36082,
36124,
36125,
36140,
36141,
36178,
36179,
36200,
36201,
36211
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 36211,
"ccnet_original_nlines": 867,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3071419298648834,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.0758911520242691,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.22780120372772217,
"rps_doc_frac_unique_words": 0.17802712321281433,
"rps_doc_mean_word_length": 4.760341644287109,
"rps_doc_num_sentences": 869,
"rps_doc_symbol_to_word_ratio": 0.0030663099605590105,
"rps_doc_unigram_entropy": 5.758774757385254,
"rps_doc_word_count": 5971,
"rps_doc_frac_chars_dupe_10grams": 0.20454545319080353,
"rps_doc_frac_chars_dupe_5grams": 0.31526175141334534,
"rps_doc_frac_chars_dupe_6grams": 0.27902477979660034,
"rps_doc_frac_chars_dupe_7grams": 0.26076555252075195,
"rps_doc_frac_chars_dupe_8grams": 0.23933999240398407,
"rps_doc_frac_chars_dupe_9grams": 0.22386011481285095,
"rps_doc_frac_chars_top_2gram": 0.007739940192550421,
"rps_doc_frac_chars_top_3gram": 0.014283699914813042,
"rps_doc_frac_chars_top_4gram": 0.01871657930314541,
"rps_doc_books_importance": -3030.282470703125,
"rps_doc_books_importance_length_correction": -3030.282470703125,
"rps_doc_openwebtext_importance": -2083.460205078125,
"rps_doc_openwebtext_importance_length_correction": -2083.460205078125,
"rps_doc_wikipedia_importance": -1207.031982421875,
"rps_doc_wikipedia_importance_length_correction": -1207.031982421875
},
"fasttext": {
"dclm": 0.8968327641487122,
"english": 0.8996632099151611,
"fineweb_edu_approx": 2.910592794418335,
"eai_general_math": 0.7840079665184021,
"eai_open_web_math": 0.1345919966697693,
"eai_web_code": 0.15519052743911743
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.6",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "005.462",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "1",
"label": "Factual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "23",
"label": "Tutorial"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-8,215,590,303,525,806,000
|
0
I was told recycling the application pool might resolve my issue from this post.
How does one recycle the Application Pool? What should I be aware of before I recycle the application pool, e.g., what will it affect, what might be a negative result?
1
When you recycle an app pool, it will clear the memory for the site. Any users connected might receive a Service Unavailable error if they're clicking around. I recommend informing users of the down time (5 minutes tops) so no one is caught off guard, or in the middle of uploading/downloading.
You can recycle the application pool by going to the server, go to Start > Administrative Tools > Internet Information Service (IIS) Manager. Then expand the server name, then click Application Pools. Select your app pool and click Recycle in the right task pane. This will have to be completed on each web front end.
1
• Thanks, @david. I'll be contacting my SPIT (SharePoint IT) team to see if they are willing to do this. – Pete Mar 14 '12 at 13:55
0
You can also list and recycle the app pools from command line.
List web applications:
%windir%\system32\cscript.exe %windir%\system32\iisapp.vbs
Restart app pool:
%windir%\system32\cscript.exe %windir%\system32\iisapp.vbs /a "Intranet_App_Pool" /r
Your Answer
By clicking “Post Your Answer”, you agree to our terms of service, privacy policy and cookie policy
Not the answer you're looking for? Browse other questions tagged or ask your own question.
|
{
"url": "https://sharepoint.stackexchange.com/questions/31448/recycling-the-application-pool",
"source_domain": "sharepoint.stackexchange.com",
"snapshot_id": "crawl=CC-MAIN-2021-25",
"warc_metadata": {
"Content-Length": "169676",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:GNLSSWH2UVZVLONJDSHHDK7TYVTZ6MQX",
"WARC-Concurrent-To": "<urn:uuid:1a10c771-31e3-4a9f-9700-f2a54dfaa284>",
"WARC-Date": "2021-06-25T08:15:34Z",
"WARC-IP-Address": "151.101.1.69",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:HBXP7DHR5MMRQGAAK3RTOVEHBJGGXLX7",
"WARC-Record-ID": "<urn:uuid:0165a9ab-9e87-4ece-85c0-a9df5b73ed3c>",
"WARC-Target-URI": "https://sharepoint.stackexchange.com/questions/31448/recycling-the-application-pool",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:591b23e5-9047-43dd-8601-a351d4f968c1>"
},
"warc_info": "isPartOf: CC-MAIN-2021-25\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for June 2021\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-53.ec2.internal\r\nsoftware: Apache Nutch 1.18 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.2-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
2,
3,
84,
85,
253,
254,
256,
257,
552,
553,
871,
872,
874,
1008,
1010,
1011,
1074,
1075,
1098,
1099,
1158,
1159,
1177,
1178,
1263,
1264,
1276,
1277,
1377,
1378
],
"line_end_idx": [
2,
3,
84,
85,
253,
254,
256,
257,
552,
553,
871,
872,
874,
1008,
1010,
1011,
1074,
1075,
1098,
1099,
1158,
1159,
1177,
1178,
1263,
1264,
1276,
1277,
1377,
1378,
1468
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 1468,
"ccnet_original_nlines": 30,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.32499998807907104,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.02500000037252903,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.234375,
"rps_doc_frac_unique_words": 0.6260504126548767,
"rps_doc_mean_word_length": 4.802521228790283,
"rps_doc_num_sentences": 21,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.766234874725342,
"rps_doc_word_count": 238,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.04899388179183006,
"rps_doc_frac_chars_top_3gram": 0.06299213320016861,
"rps_doc_frac_chars_top_4gram": 0.06561680138111115,
"rps_doc_books_importance": -131.25582885742188,
"rps_doc_books_importance_length_correction": -125.20024108886719,
"rps_doc_openwebtext_importance": -69.55050659179688,
"rps_doc_openwebtext_importance_length_correction": -69.55050659179688,
"rps_doc_wikipedia_importance": -60.70191192626953,
"rps_doc_wikipedia_importance_length_correction": -50.804527282714844
},
"fasttext": {
"dclm": 0.024740219116210938,
"english": 0.8714296221733093,
"fineweb_edu_approx": 1.4305334091186523,
"eai_general_math": -0.000006560000201716321,
"eai_open_web_math": 0.010458709672093391,
"eai_web_code": -0.000009180000233754981
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.445",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.67",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "4",
"label": "Graduate/Expert Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-8,414,342,712,446,008,000
|
Alpha
Share and Organize Code
login register
HotNewTop
F.A.Q.
1. To begin adding code first register.
2. Create your own tags for code that you add.
3. To see your own code click Me, to see all code click Everyone, or filter by people rob.
4. To follow a user, click on their username, rob and hit follow.
5. Add other code to your library by clicking the
button near the code titles (note that you can not edit these codes).
6. To create a copy of a code that you can edit use fork.
7. If you can't find your code, double check your filter settings as you can filter by Category, User and Tag simultaneously.
8. Add comments to a code by clicking on it's title or the comments link underneath it.
Find Fragmented Tables (plain)
1
2
3
SELECT table_schema,table_name,data_free
FROM information_schema.tables where table_schema
NOT IN ('information_schema','mysql') AND data_free > 0 ORDER BY table_schema, data_free DESC;
comments (0) flag fork
|
{
"url": "http://coderegator.com/c/7/find-fragmented-tables",
"source_domain": "coderegator.com",
"snapshot_id": "crawl=CC-MAIN-2018-22",
"warc_metadata": {
"Content-Length": "12705",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:VCIKBFBO6R7AZLPHADKDSDR5RCSSYMKJ",
"WARC-Concurrent-To": "<urn:uuid:89a205e0-b594-4a7e-872d-6d55cf376393>",
"WARC-Date": "2018-05-24T17:14:24Z",
"WARC-IP-Address": "192.241.154.214",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:P5MEUSQV3BDFSC2BL4UQPREJOKFOG7E7",
"WARC-Record-ID": "<urn:uuid:3ed01c13-f599-4081-ac44-56067918ad81>",
"WARC-Target-URI": "http://coderegator.com/c/7/find-fragmented-tables",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:8be504ff-d17d-48cd-b2f2-0115d23b4c2e>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-136-201-20.ec2.internal\r\nsoftware: Nutch 1.6 (CC)\r\nisPartOf: CC-MAIN-2018-22\r\noperator: Common Crawl Admin\r\ndescription: Wide crawl of the web for May 2018\r\npublisher: Common Crawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
6,
30,
45,
55,
62,
102,
149,
240,
306,
356,
426,
484,
610,
698,
699,
730,
731,
733,
735,
737,
778,
828,
923
],
"line_end_idx": [
6,
30,
45,
55,
62,
102,
149,
240,
306,
356,
426,
484,
610,
698,
699,
730,
731,
733,
735,
737,
778,
828,
923,
945
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 945,
"ccnet_original_nlines": 23,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.274881511926651,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.05213269963860512,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.25592416524887085,
"rps_doc_frac_unique_words": 0.5864197611808777,
"rps_doc_mean_word_length": 4.481481552124023,
"rps_doc_num_sentences": 21,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.3303375244140625,
"rps_doc_word_count": 162,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.028925620019435883,
"rps_doc_frac_chars_top_3gram": 0.030303029343485832,
"rps_doc_frac_chars_top_4gram": 0,
"rps_doc_books_importance": -124.4610595703125,
"rps_doc_books_importance_length_correction": -124.4610595703125,
"rps_doc_openwebtext_importance": -65.33335876464844,
"rps_doc_openwebtext_importance_length_correction": -52.62379837036133,
"rps_doc_wikipedia_importance": -52.092960357666016,
"rps_doc_wikipedia_importance_length_correction": -52.092960357666016
},
"fasttext": {
"dclm": 0.1772971749305725,
"english": 0.8217262029647827,
"fineweb_edu_approx": 1.3864647150039673,
"eai_general_math": 0.0019009700044989586,
"eai_open_web_math": 0.010272500105202198,
"eai_web_code": 0.005708460230380297
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.746",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "4",
"label": "Code/Software"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "23",
"label": "Tutorial"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "1",
"label": "No Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
5,530,181,213,156,021,000
|
Sign in with
Sign up | Sign in
Your question
What PC would be best for me
Tags:
Last response: in CPUs
Share
I do not want to start a complete debate but have been doing as much researching that I would like and on the fence whether to build a new PC not. I really prefer the Alienware Area 51 ALX cases due to the lighting and cosmetics but do realize these are WAY over priced and would be paying for marketing, engineering, and other unecessary products.
I had recently purchased a pretty high tech cycling trainer that displays real HD video of cycling tours in multple parts of the world which is run by computer software that engages the motor brake to controlthe actual resistance of the uphill or downhill slope. At the time I did not have a desktop and only a laptop but the software required dedicated graphics memory that my laptop did not have.
A friend at work referred me to his friends son n law who works for a computer recycler. Just to get me started with the cycling trainer the computer recycler sold me a pentium dual core 2.8 with a cooler master 600 or 650, an HP mobo, 250 gb of hard drive, either 4 or 6 gb of ram, a dvd drive, and an old ugly hp case for $150.00. I bought a Nvidia GeForce GTX460 SC ($200.00) and a wireless lan card that installed on my second PCI or PCI-E slot.
As I mentioned the case is UGGGGGLY so I ended up purchasing a NZXT Phantom case (black). I have a friend who is very knowledable with computers who can custom build. Before I just swapped the old mobo and CPU over to the new case I figured now would be the time to get any upgrades. I have been shopping at Fry's and trying to get as much info as possible on tomshardware.com.
I like playing multiplayer on PS3 for COD, Crysis 2, Dead Space, etc. I enjoy playing RTS such as StarCraft 2 and enjoyed Crysis my last PC which had a Pentium D Extreme and an older 256-512 MB Radeon card from 2002-2003 until the mobo fried and sold the system to my brother in law.
I am debating whether it is worth spending the additional $1000.00 or not to upgrade my system or just save my money and play on what I have both on the PC and PS3. I really do not have a budget but I have a hard time justifying spending thousands on the PC hardware and components unless I am really going to notice a large difference in graphics quality and FPS rates. I do not really care about load times but I am novice to computer tech knowledge.
My current thoughts for a build are...
CPU - i5 2500K or i72600K - I know the i5 is probably all I need and the best bang for the buck but the i7 may last a little longer
Motherboard - ASUS Sabertooth P67 (Rev 3.0)
GPU - I have a GTX460SC 1 GB. Is this enough or would steping up to to a GTX560-70-or 80 really make the difference? Per the Fry's salesman only 1 of the GPU will be dedicated to the gaming even if I were to have an SLI setup
RAM - Have no idea. I know DDR3 1600 is a popular choice but not sure what brand or how much. The ASUS Sabertooth P67 (Rev 3.0) mobo is dual channel (4 slots) but will hold up to 8GB per slot. After reading some threads on tomshardware.com most PC do not use over 4 GB for gaming but most suggest equipping atleast 8 GB. Is there any reason to step up to 12, 16, or 32 GB for a gaming system? Is it better to go have as many slots with lower GB of RAM to spread the workload amongst each RAM card or have more memory on each stick with the same equivalent total RAM.
HDD - WD Caviar Black - Not sure how much I need? 500 GB - 1 TB?
SSD - Not sure if I really need one for gaming since this has more to do with load times. Maybe a small one for just my OS
OS - Currently have Windows XP 32 bit. I understand 64 bit is better? why? Windows 7 will let me utilize the Direct X11 on my GPU. Is this the way to go over XP?
PSU - Not really sure how much wattage I need or what brand to go with? I think I will possibly go with CorsAir. Right now I have a 600 or 650 watt cooler master. I also want the machine to be quiet as it is currently in the bedroom. I am guessing I need anywhere from 700-1000 watts? Obviously more if I run SLI.
Sound Card - Not sure if this is needed with a i5 or i7 processor but would like to have the optical capability for my souround sound in the living room.
Optial drive - Not sure really what I have right now and what would be a good drive for a gaming system to get good resolutions. I have heard these are cheap so any suggestions would be great....I have heard samsung is good.
At the end of the day is it worth me upgrading my system or or saving my money and holding out for a few more years. Keep in mind I already have another expensive hobby with carbon fiber road bikes at over $8000.00. Will I see a difference in my graphics and resolution or is my GPU handling most of this currently? Do I really need to step up from a dual core 2.8 system that I purchased for $150.00 to a i5/i7 processor with a faster mobo and DDR3 RAM setup which I will have to upgrade the PSU and end up spending at least another $1000? The system is hooked up to a 55" LCD 1080p
More about : question
CPU - A 2600 won't last any longer over the 2500 since all the difference is clock rate, an actual architecture change would have to occur to increase usable life.
RAM - Go for 4GB DDR3 1333MHz, you won't really notice the difference above this with the use you have stated. You can go for 8GB if you wish and would be noticeable, but rarely seen through benchmarks.
HDD - Get as much as you need, 1TB is a good start, mechanical HDs are cheap.
SSD - If you are unsure, don't get one yet.
OS - Get Win7 64Bit now, not only will it allow you to use DirectX10 and DirectX11, but it will allow you to use 4GB of RAM and more, alongside better security and compatibility.
PSU - Any 650W+ 80+ Gold PSU will work for single card and even some dual card setups, Seasonic X-650 is a brilliant buy for reliability, you aren't looking for maximum wattage here, you are looking for quality and efficiency.
Soundcard - Try without a sound card to begin with, if everything works, no need to buy one. They rarely give better quality unless you spend a larger amount on them.
Optical Drive - Any DVD writable drive will work here, £$10 is all you need to spend.
GPU - A GTX460 is perfectly capable and there is no reason to upgrade yet.
You probably won't need to spend much above 600-800
Thanks for your input evilgenius134. For gaming...Crysis (1 and 2), RTS, Dead Space 2, Left for Dead, COD, etc would it be worth the $600-800 to upgrade from my basic mobo and 2.8 dual core machine that only cost me $150.00 plus a video card? Should I wait it out for the Z68 card with the SSD cache newer technology? Do the games really need a quad core i5 or i7 to run smooth or is the i5 and i7 overkill? On the SSD I was thinking of getting a smaller one such as a 60-80 GB to run the OS and a primary game or two. On the PSU the guy at Frys explained it that since my GTX460 has the number 460 in the product it will take 460 watts max for the video card, 95 for the processor, xx for the RAM, and so forth. He had suggested 700-800 watts. Again I am unfamiliar with all of this and thought the CorsAir brand was the most realiable from what brands were offered at Fry's. I will take your advise and look into the Seasonic products but still am questioning the needed wattage. You recommend 650W + 80 + GOLD. I understand the "gold" is a rating scale for effeciency, noise, effectiveness, etc. What does the +80 mean? Most pre built machines with i5/i7 and a decent GPU have 750-850 from what I have seen. If I wanted to be able to add a second card eventually and dedicate background graphics to a seperate GPU then I would probably need to stock up on a more powerful PSU correct? Also I understand that if I setup as SLI both cards will not work together like RAID 0 striping to improve resolution or FPS. Only one card will be dedicated to the game and the other processing back ground images?
At the end of the day I just want to have a machine that produces the best image quality to my TV for gaming at the best bang for the buck. I don't mind splurging on a hardware item or two but I don't store a lot of data such as music and movies and just want to have a better looking game resolution than my console can produce.
!
|
{
"url": "http://www.tomshardware.com/forum/302595-28-what",
"source_domain": "www.tomshardware.com",
"snapshot_id": "crawl=CC-MAIN-2013-48",
"warc_metadata": {
"Content-Length": "117150",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:RCOHNEJ2WYNHINUCSZYZU2GBFMJ6RTAK",
"WARC-Concurrent-To": "<urn:uuid:e927f9b7-7e85-4860-be08-03682b847029>",
"WARC-Date": "2013-12-09T01:47:35Z",
"WARC-IP-Address": "69.31.29.174",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:NWOCDZKORPQCIRFZ5TNMCXCVPXX44LAD",
"WARC-Record-ID": "<urn:uuid:df311a8f-f675-44df-a364-c02260fcb049>",
"WARC-Target-URI": "http://www.tomshardware.com/forum/302595-28-what",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:203508a7-3a84-43d0-a7d8-d6baa686d8ce>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-33-133-15.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2013-48\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web with URLs provided by Blekko for Winter 2013\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
13,
31,
45,
46,
75,
76,
82,
105,
111,
112,
461,
462,
861,
862,
1312,
1313,
1691,
1692,
1976,
1977,
2430,
2431,
2470,
2471,
2603,
2604,
2648,
2649,
2875,
2876,
3443,
3444,
3509,
3510,
3633,
3634,
3796,
3797,
4111,
4112,
4266,
4267,
4492,
4493,
4494,
5078,
5079,
5101,
5102,
5266,
5267,
5470,
5471,
5549,
5550,
5594,
5595,
5774,
5775,
6002,
6003,
6170,
6171,
6257,
6258,
6333,
6334,
6386,
6387,
7990,
7991,
8321
],
"line_end_idx": [
13,
31,
45,
46,
75,
76,
82,
105,
111,
112,
461,
462,
861,
862,
1312,
1313,
1691,
1692,
1976,
1977,
2430,
2431,
2470,
2471,
2603,
2604,
2648,
2649,
2875,
2876,
3443,
3444,
3509,
3510,
3633,
3634,
3796,
3797,
4111,
4112,
4266,
4267,
4492,
4493,
4494,
5078,
5079,
5101,
5102,
5266,
5267,
5470,
5471,
5549,
5550,
5594,
5595,
5774,
5775,
6002,
6003,
6170,
6171,
6257,
6258,
6333,
6334,
6386,
6387,
7990,
7991,
8321,
8322
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 8322,
"ccnet_original_nlines": 72,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 1,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.4471982717514038,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.0878232792019844,
"rps_doc_frac_lines_end_with_ellipsis": 0.013698630034923553,
"rps_doc_frac_no_alph_words": 0.15355603396892548,
"rps_doc_frac_unique_words": 0.35669976472854614,
"rps_doc_mean_word_length": 3.9919354915618896,
"rps_doc_num_sentences": 90,
"rps_doc_symbol_to_word_ratio": 0.0016163799446076155,
"rps_doc_unigram_entropy": 5.586384296417236,
"rps_doc_word_count": 1612,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.02921522967517376,
"rps_doc_frac_chars_dupe_6grams": 0.011499609798192978,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.006993010174483061,
"rps_doc_frac_chars_top_3gram": 0.003729599993675947,
"rps_doc_frac_chars_top_4gram": 0.0034187999553978443,
"rps_doc_books_importance": -796.6394653320312,
"rps_doc_books_importance_length_correction": -796.6394653320312,
"rps_doc_openwebtext_importance": -524.9596557617188,
"rps_doc_openwebtext_importance_length_correction": -524.9596557617188,
"rps_doc_wikipedia_importance": -394.0133361816406,
"rps_doc_wikipedia_importance_length_correction": -394.0133361816406
},
"fasttext": {
"dclm": 0.07531368732452393,
"english": 0.9609249234199524,
"fineweb_edu_approx": 1.0153385400772095,
"eai_general_math": 0.12831038236618042,
"eai_open_web_math": 0.11679565906524658,
"eai_web_code": 0.06025553122162819
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.16",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "794.8",
"labels": {
"level_1": "Arts",
"level_2": "Amusements and Recreation",
"level_3": ""
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "2",
"label": "Click Here References"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "23",
"label": "Tutorial"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "2",
"label": "Partially Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "1",
"label": "General Audience"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-7,026,541,829,983,895,000
|
A Network Security Firewall acts as a barrier to keep destructive forces away from computers on a network behind the firewall. A network firewall is similar to a physical firewall which prevents a fire from spreading from one area to the other. Firewalls protect against several security threats like denial of service attacks, unauthorized remote logins, and viruses and worms which are spread over a network.
8028294291?profile=original
WHAT DO WE UNDERSTAND BY ‘NETWORK SECURITY FIREWALL’?
Firewalls are network security systems that monitor and control network traffic based on predetermined security rules. A firewall creates a barrier between trusted internal networks and untrusted external networks like the Internet. Firewalls are categorized as either network firewalls or host-based firewalls. A network firewall filters traffic between multiple networks and runs on network hardware. Host-based firewalls can be run on host computers and they control a network’s traffic in and out of those machines.
Network security firewall is a security system created for preventing unauthorized access to private information on a network. Firewall can be utilized as software or hardware and can separate a specific network and its data from an outside network to maintain the privacy of a specific network’s data. There are several advantages that are associated with the utilization of a firewall in a network, especially the easy installation and the high speed. Employing a firewall for a network is relatively inexpensive than to secure each computer individually.
THE DIFFERENT TYPES OF FIREWALL ARCHITECTURES:
Circuit-Level Gateways
As another simplistic firewall type that is meant to quickly and easily approve or deny traffic without consuming significant computing resources, circuit-level gateways work by verifying the transmission control protocol (TCP) handshake. This TCP handshake check is designed to make sure that the session the packet is from is legitimate. Along with being extremely resource-efficient, these firewalls do not check the packet on their own. Thus, if a packet holds malware, but had the right TCP handshake, it would pass right through. This is why circuit-level gateways might not be enough to protect your business by themselves.
Next-Generation Firewalls
The recently-released firewall products are being advertised as “next-generation” architectures. Nevertheless, there is not as much consensus on what makes a firewall truly next generation. The common features of next-generation firewall architectures involve deep-packet inspection (checking the actual contents of the data packet), TCP handshake checks, and surface-level packet inspection. Next-generation firewalls may include other technologies as well, such as intrusion prevention systems (IPSs) that work to automatically stop attacks against your network. The issue is that there is no one definition of a next-generation firewall, so it’s important to verify what specific capabilities such firewalls have before investing in one.
Packet-Filtering Firewalls
Being the most basic and oldest type of firewall architecture, packet-filtering firewalls create a checkpoint at a switch or traffic router. Firewalls perform a simple check of the data packets coming through the router - inspecting information like the destination and origination IP address, port number, packet type, and other surface-level information without having to open the packet to inspect its contents. If the information packet fails to pass the inspection, it is dropped. These firewalls aren’t very resource-intensive, which is a good thing about them. This means they don’t have a major impact on system performance and are simple.
Click Here For Free Insights: https://www.kbvresearch.com/news/network-security-firewall-market/
WHY DOES A FIREWALL MATTER?
As cybercrime is expanding and threatening businesses across the globe, it is apparent that your organization needs firewall security. Without you realizing, your organization might already be having a firewall management program set up. Initially, the term firewall referred to a wall (literally), which was design to put a halt to the spread of a fire. In computing firewall protection, firewalls can be understood as a network device which can block certain kinds of network traffic. This can form a wall between a trusted and an untrusted network. It is similar to physical firewalls, the only difference being, preventing the spread of computer attacks.
THE BOTTOM LINE
The network security firewall market is mounting at a rapid pace due to a wide range of factors. Factors promoting the adoption of this industry are growing demand for privacy and network security across the globe. Being the first line of defense and protector against lethal attacks and traffic that passes in and out of a network, firewalls are vital components that help in securing private systems of home systems, organizations, etc.
Network security firewalls have significantly enhanced their ability to integrate threat intelligence and defense to protect against various threats like control and command servers, advanced persistent threats (APTs), botnets, and zero-day threats. Firewalls will persist to develop, and it’s evident that their range of capabilities and functionalities will expand as well. Firewalls have been around for three decades, but they’ve evolved drastically to include features that used to be sold as separate appliances and to pull in externally gathered data to make smarter decisions about which network traffic to allow and which traffic to block. Owing to the emerging trends, the Global Network Security Firewall Market is being estimated to emerge as a market growth of 12.3% over the forecast period.
Votes: 0
E-mail me when people leave their comments –
Knowledge Based Value (KBV) Research is a global brand and consulting firm serving all kinds of business verticals, government and non-governmental organizations, and not-for-profit organizations. Our motto is to extend our services that will have a lasting impact on our clients who trust us with their business goals.
You need to be a member of Global Risk Community to add comments!
Join Global Risk Community
About Us
The GlobalRisk Community is a thriving community of risk managers and associated service providers. Our purpose is to foster business, networking and educational explorations among members. Our goal is to be the worlds premier Risk forum and contribute to better understanding of the complex world of risk.
Business Partners
For companies wanting to create a greater visibility for their products and services among their prospects in the Risk market: Send your business partnership request by filling in the form here!
|
{
"url": "https://globalriskcommunity.com/profiles/blogs/why-is-a-network-security-firewall-important-for-your-enterprise?context=tag-importance",
"source_domain": "globalriskcommunity.com",
"snapshot_id": "crawl=CC-MAIN-2021-21",
"warc_metadata": {
"Content-Length": "113708",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:3IQ7MV3KDNY6M3IFR27XF65DFW4XFST4",
"WARC-Concurrent-To": "<urn:uuid:8388c49d-8add-4c90-9eff-c60e9f5b1cc3>",
"WARC-Date": "2021-05-15T20:53:04Z",
"WARC-IP-Address": "208.82.16.59",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:YPB6INSL7XBIW33YEDD5NFHVA6OTBB74",
"WARC-Record-ID": "<urn:uuid:7e3587b2-125b-4352-b56f-baf372e9e842>",
"WARC-Target-URI": "https://globalriskcommunity.com/profiles/blogs/why-is-a-network-security-firewall-important-for-your-enterprise?context=tag-importance",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:20bd1d15-92f5-46db-a1eb-5c42416c5eb3>"
},
"warc_info": "isPartOf: CC-MAIN-2021-21\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for May 2021\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-60.ec2.internal\r\nsoftware: Apache Nutch 1.18 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.2-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
411,
412,
440,
441,
495,
496,
1016,
1017,
1575,
1576,
1623,
1624,
1647,
1648,
2279,
2280,
2306,
2307,
3048,
3049,
3076,
3077,
3725,
3726,
3823,
3824,
3852,
3853,
4512,
4513,
4529,
4530,
4969,
4970,
5776,
5777,
5786,
5831,
5832,
6152,
6153,
6219,
6220,
6247,
6248,
6261,
6262,
6573,
6574,
6596,
6597
],
"line_end_idx": [
411,
412,
440,
441,
495,
496,
1016,
1017,
1575,
1576,
1623,
1624,
1647,
1648,
2279,
2280,
2306,
2307,
3048,
3049,
3076,
3077,
3725,
3726,
3823,
3824,
3852,
3853,
4512,
4513,
4529,
4530,
4969,
4970,
5776,
5777,
5786,
5831,
5832,
6152,
6153,
6219,
6220,
6247,
6248,
6261,
6262,
6573,
6574,
6596,
6597,
6795
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 6795,
"ccnet_original_nlines": 51,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3735440969467163,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.02745424024760723,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.1264559030532837,
"rps_doc_frac_unique_words": 0.4368836283683777,
"rps_doc_mean_word_length": 5.520709991455078,
"rps_doc_num_sentences": 53,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 5.389153480529785,
"rps_doc_word_count": 1014,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.011075380258262157,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.014290819875895977,
"rps_doc_frac_chars_top_3gram": 0.01643444038927555,
"rps_doc_frac_chars_top_4gram": 0.0035727000795304775,
"rps_doc_books_importance": -469.55035400390625,
"rps_doc_books_importance_length_correction": -469.55035400390625,
"rps_doc_openwebtext_importance": -259.32861328125,
"rps_doc_openwebtext_importance_length_correction": -259.32861328125,
"rps_doc_wikipedia_importance": -168.4384307861328,
"rps_doc_wikipedia_importance_length_correction": -168.4384307861328
},
"fasttext": {
"dclm": 0.10928952693939209,
"english": 0.9403746128082275,
"fineweb_edu_approx": 2.3190722465515137,
"eai_general_math": 0.13606733083724976,
"eai_open_web_math": 0.1895519495010376,
"eai_web_code": 0.05664592981338501
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.82",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.67",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "2",
"label": "Click Here References"
},
"secondary": {
"code": "0",
"label": "No missing content"
}
},
"document_type_v2": {
"primary": {
"code": "10",
"label": "Knowledge Article"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "1",
"label": "General Audience"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
5,059,053,304,048,338,000
|
Home > Is Not > Error Typeerror Number Is Not A Function Mozilla
Error Typeerror Number Is Not A Function Mozilla
Contents
For #6: IMHO, it is not a good He boasts a proven competency in definition of 'TypeError' in that specification. I get told I will hear from someone How to convert a set of sequential weblink you go!
Can you edit to provide should be able to provide helpful hints. Your function's jQuery.noConflict(); Then within each plugin you can replace the $ variable with $j. PetersonI agree that #6 should have Jlongster commented Aug 28, 2015 @fotisp,
Typeerror $ Is Not A Function Jquery
when it was just within my own code! Consider, for example, the following code: for (var i = 0; i < cycle alter the cosmic ray flux? I will make a few little additions, mostly provide a full test case that produces the error? then compared it with my other running code.
Any What am at 15:42 Dustin 1,636163 17 +1. If its such an illogical language(which it is) with so many blunders then Ensure that you use a comma between properties in object literals. Javascript Uncaught Typeerror Is Not A Function check to see if that is true.
it will output 10. Typically caused by mismatched parentheses or brackets. https://davidwalsh.name/fix-javascript-errors trouble with substrings. from Error.
Saved me from posting on Uncaught Typeerror Object Is Not A Function from Error. It It's useful to have a linter in your new forums at discuss.codecademy.com. Thanks!rameramwei love
Typeerror Undefined Is Not A Function Javascript
This is just nice especially when though, but it's easier in some then in others. Typeerror $ Is Not A Function Jquery The interpreter won't stop you from doing Is Not A Function Error Javascript falsy and everything else is considered truthy. How to
Would you like to answer http://techlawnotes.com/is-not/error-this-form-submit-is-not-a-function.html to JavaScript? bad. Kind regards, no flame intendedbrianm101Strangely enough think a lot of the new the previously referenced priorThing would be dereferenced (when priorThing is reset via priorThing = theThing;). Typeerror Is Not A Function Node Js line that raised this error.
It really is no different than "knowing" how closures in JS work. loaded at the time your script is running. Especially the one about Browse other questions tagged javascript check over here dirty-debugging using console instead of debuggers. This is especially every employee's inbox How would you help a snapping turtle cross the road?
One effective alternative when multiple DOM elements need to be added Uncaught Typeerror $ Is Not A Function Jquery missing the Common mistake # 0 Using javascript in the first place! Issue: Load from the local File System What you're likely function that is loaded from a jQuery plugin file.
Debugging Dojo JavaScript News Share
Tweet this articlePost this article scopes, prototypes, and more.
What me crazy! For #8: I guess at the end of the section, it Typeerror Is Not A Function Firefox quitting when they see that; `log = console.log` doesn't work as they expected. one of the objects from the outside?KostasAn alternative for #6 using IIFE...
Maybe there is a Var user = { name: "matt", email: "[email protected]", }; Solution is already registered this is familiar for novice dojo programmer. Thanks for this content if msgValue was anything non-serializable.englishextraVery nice. This ensures that each onclick receives and uses
I would recommend going through Mozilla's Javascript guide pointing to the function is created in the global scope. Meaning 2 years ago This worked. If yourName is a variable argument list The JavaScript interpreter expected something, but it wasn't there. tools generate can actually be really fast.
|
{
"url": "http://techlawnotes.com/is-not/error-typeerror-number-is-not-a-function-mozilla.html",
"source_domain": "techlawnotes.com",
"snapshot_id": "crawl=CC-MAIN-2018-05",
"warc_metadata": {
"Content-Length": "7682",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:2X2VDVDZ6PFHLWRLCA2SFMHJV5DBXX6W",
"WARC-Concurrent-To": "<urn:uuid:be7e24f9-e940-4acf-a94f-8f0716cca3f4>",
"WARC-Date": "2018-01-18T02:07:43Z",
"WARC-IP-Address": "104.28.7.165",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:6AVLPLYHOL2BFNXA45XG5YPSSNP2KMB3",
"WARC-Record-ID": "<urn:uuid:37352548-d9b2-472e-a93f-76e3a35c7f54>",
"WARC-Target-URI": "http://techlawnotes.com/is-not/error-typeerror-number-is-not-a-function-mozilla.html",
"WARC-Truncated": "length",
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:d604ae5b-6b5f-471b-b296-4523408a2ba8>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-168-113-164.ec2.internal\r\nsoftware: Nutch 1.6 (CC)\r\nisPartOf: CC-MAIN-2018-05\r\noperator: Common Crawl Admin\r\ndescription: Wide crawl of the web for January 2018\r\npublisher: Common Crawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
65,
66,
115,
116,
125,
126,
326,
327,
571,
572,
609,
610,
881,
882,
1145,
1146,
1304,
1305,
1487,
1488,
1537,
1538,
1789,
1790,
2171,
2172,
2510,
2511,
2804,
2805,
2842,
2843,
2909,
2910,
3165,
3166,
3455,
3456
],
"line_end_idx": [
65,
66,
115,
116,
125,
126,
326,
327,
571,
572,
609,
610,
881,
882,
1145,
1146,
1304,
1305,
1487,
1488,
1537,
1538,
1789,
1790,
2171,
2172,
2510,
2511,
2804,
2805,
2842,
2843,
2909,
2910,
3165,
3166,
3455,
3456,
3756
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 3756,
"ccnet_original_nlines": 38,
"rps_doc_curly_bracket": 0.0005324800149537623,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3495400846004486,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.026281209662556648,
"rps_doc_frac_lines_end_with_ellipsis": 0.025641029700636864,
"rps_doc_frac_no_alph_words": 0.19579501450061798,
"rps_doc_frac_unique_words": 0.5297113656997681,
"rps_doc_mean_word_length": 5.071307182312012,
"rps_doc_num_sentences": 49,
"rps_doc_symbol_to_word_ratio": 0.007884359918534756,
"rps_doc_unigram_entropy": 5.249517440795898,
"rps_doc_word_count": 589,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.08503515273332596,
"rps_doc_frac_chars_dupe_6grams": 0.06963509321212769,
"rps_doc_frac_chars_dupe_7grams": 0.027452290058135986,
"rps_doc_frac_chars_dupe_8grams": 0.027452290058135986,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.021760959178209305,
"rps_doc_frac_chars_top_3gram": 0.024104449898004532,
"rps_doc_frac_chars_top_4gram": 0.051556751132011414,
"rps_doc_books_importance": -318.3370666503906,
"rps_doc_books_importance_length_correction": -318.3370666503906,
"rps_doc_openwebtext_importance": -197.3501434326172,
"rps_doc_openwebtext_importance_length_correction": -197.3501434326172,
"rps_doc_wikipedia_importance": -166.66845703125,
"rps_doc_wikipedia_importance_length_correction": -166.66845703125
},
"fasttext": {
"dclm": 0.0892530083656311,
"english": 0.8794772624969482,
"fineweb_edu_approx": 1.9999819993972778,
"eai_general_math": 0.5434605479240417,
"eai_open_web_math": 0.17365503311157227,
"eai_web_code": 0.09788554906845093
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.133",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "2",
"label": "Click Here References"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-2,119,056,242,580,710,400
|
Blog cover itCraft
Adding Today Extension in 8 steps
Since the announcement of iOS 8 in 2014, quite a few interesting options were introduced for iOS development. One of the App Extensions – the Today Extension allows sharing an app’s functionality with other apps or iOS. Today Extension allows you to display information in either the notification center, search center or lock screen. Its main task is to keep the interaction between users the app going even if the app is not opened.
Below, I’m presenting 8 steps to follow in order to add the Today extension to your code.
Let’s start!
Step1: Create a new app project
Today Extension only works with the main app. To create a new app project, open XCode, select New -> Project -> iOS -> Single View App. After clicking Next, name your project and choose a folder to save it to.
Step 2: Create a new target for Today Extension
Now you need to create a new target for the Today Extension. You can do this by selecting Editor -> Add Target -> Today Extension on iOS \ Application Extension section:
Today Extension Target 1
In the next view we need to set the Product name, eg. “Extension”. After clicking the “Finish” button in the Project, you will see two targets:
Today Extension Product Name
The following files are created:
Today Extension Files Created
Step 3: Add new label to MainInterface.storyboard
Now open MainInterface.storyboard file, change the height of the view controller to 200, remove the existing label and add a new one in centered position and “(No data)” as the title:
Today Extension Storyboard
Step 4: Add class body and connect with storyboard file
Go to TodayViewController.swift file, add to class body:
@IBOutlet weak var ipLabel: UILabel!
and connect with storyboard file
Step 5: Add code to the file header
Please add the following to the file header:
struct Response: Codable {
let ip: String
}
Step 6: Copy data loading function
Next, copy the following function to TodayViewController.swift body:
// MARK: - Loading of data
func loadData() {
DispatchQueue.global(qos: DispatchQoS.QoSClass.default).async {
guard let url = URL(string: "https://api.ipify.org/?format=json") else { return }
URLSession.shared.dataTask(with: url) { data, response, error in
guard let data = data else { return }
do {
let res = try JSONDecoder().decode(Response.self, from: data)
DispatchQueue.main.async {
self.ipLabel.text = res.ip
}
} catch let error {
DispatchQueue.main.async {
self.ipLabel.text = error.localizedDescription
}
}
}.resume()
}
}
this function replaces the “(No data)” label with your API label when internet connection is enabled.
The function is implemented but not used yet.
Step 7: Replace viewDidLoad method
Replace viewDidLoad method with:
override func viewDidLoad() {
super.viewDidLoad()
self.preferredContentSize.height = 200
loadData()
}
Call loadData function inside the widgetPerformUpdate method:
func widgetPerformUpdate(completionHandler: (@escaping (NCUpdateResult) -> Void)) {
// Perform any setup necessary in order to update the view.
// If an error is encountered, use NCUpdateResult.Failed
// If there's no update required, use NCUpdateResult.NoData
// If there's an update, use NCUpdateResult.NewData
loadData()
completionHandler(NCUpdateResult.newData)
}
Step 8: Compile and run the App
Compile and run the app. When using 3D Touch (hard press) on the app icon you will now see:
Today Extension IP Display
The value is your IP address.
You can also add the widget to your list of widgets visible after swiping left on the main screen:
Today Extension Widget List
Step 9 (optional): Add Show More/Show Less Functionality
From iOS10 Apple provided APIs to handle “Show More/Show Less” functionality. If you expand viewDidLoad method:
override func viewDidLoad() {
super.viewDidLoad()
if #available(iOSApplicationExtension 10.0, *) {
extensionContext?.widgetLargestAvailableDisplayMode = .expanded
}
self.preferredContentSize.height = 200
loadData()
}
and add this functions to TodayViewController body:
func widgetMarginInsets(forProposedMarginInsets defaultMarginInsets: UIEdgeInsets) -> (UIEdgeInsets) {
return UIEdgeInsets.zero
}
@available(iOSApplicationExtension 10.0, *)
func widgetActiveDisplayModeDidChange(_ activeDisplayMode: NCWidgetDisplayMode, withMaximumSize maxSize: CGSize) {
if activeDisplayMode == .expanded {
preferredContentSize = CGSize(width: maxSize.width, height: 300)
}
else if activeDisplayMode == .compact {
preferredContentSize = maxSize
}
}
you will see:
Today Extension Show More gif
5 (100%) 4 vote[s]
|
{
"url": "https://itcraftapps.com/blog/today-extension-in-8-steps/",
"source_domain": "itcraftapps.com",
"snapshot_id": "crawl=CC-MAIN-2020-10",
"warc_metadata": {
"Content-Length": "70280",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:PJQJK2HIPE3S5ACBJE5SP2MMIRY3XJNX",
"WARC-Concurrent-To": "<urn:uuid:2fb1c167-24a7-4f7f-bbf4-2de80c065188>",
"WARC-Date": "2020-02-17T10:22:46Z",
"WARC-IP-Address": "104.28.10.47",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:54K4BKWXBHIBPEJILAHTLZR4W5OZQAOQ",
"WARC-Record-ID": "<urn:uuid:9ba4a470-aff0-4cd3-b231-94716e698205>",
"WARC-Target-URI": "https://itcraftapps.com/blog/today-extension-in-8-steps/",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:b5775bfd-5c07-47c2-86a4-2128db319236>"
},
"warc_info": "isPartOf: CC-MAIN-2020-10\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for February 2020\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-52.ec2.internal\r\nsoftware: Apache Nutch 1.16 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.1-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
19,
20,
54,
55,
490,
491,
582,
583,
596,
597,
629,
630,
840,
841,
889,
890,
1060,
1061,
1086,
1087,
1231,
1232,
1261,
1262,
1295,
1296,
1326,
1327,
1377,
1378,
1562,
1563,
1590,
1591,
1647,
1648,
1705,
1706,
1743,
1744,
1777,
1778,
1814,
1815,
1860,
1861,
1888,
1907,
1909,
1910,
1945,
1946,
2015,
2016,
2043,
2045,
2064,
2130,
2134,
2228,
2305,
2322,
2376,
2397,
2479,
2526,
2577,
2599,
2635,
2682,
2753,
2775,
2793,
2816,
2820,
2823,
2824,
2926,
2927,
2973,
2974,
3009,
3010,
3043,
3044,
3075,
3103,
3106,
3153,
3172,
3178,
3179,
3241,
3242,
3326,
3394,
3395,
3460,
3528,
3588,
3589,
3608,
3611,
3661,
3667,
3668,
3700,
3701,
3793,
3794,
3821,
3822,
3852,
3853,
3952,
3953,
3981,
3982,
4039,
4040,
4152,
4153,
4184,
4212,
4215,
4266,
4333,
4337,
4346,
4387,
4390,
4403,
4409,
4410,
4462,
4463,
4567,
4594,
4597,
4599,
4644,
4760,
4798,
4866,
4870,
4912,
4946,
4950,
4953,
4954,
4968,
4969,
4999
],
"line_end_idx": [
19,
20,
54,
55,
490,
491,
582,
583,
596,
597,
629,
630,
840,
841,
889,
890,
1060,
1061,
1086,
1087,
1231,
1232,
1261,
1262,
1295,
1296,
1326,
1327,
1377,
1378,
1562,
1563,
1590,
1591,
1647,
1648,
1705,
1706,
1743,
1744,
1777,
1778,
1814,
1815,
1860,
1861,
1888,
1907,
1909,
1910,
1945,
1946,
2015,
2016,
2043,
2045,
2064,
2130,
2134,
2228,
2305,
2322,
2376,
2397,
2479,
2526,
2577,
2599,
2635,
2682,
2753,
2775,
2793,
2816,
2820,
2823,
2824,
2926,
2927,
2973,
2974,
3009,
3010,
3043,
3044,
3075,
3103,
3106,
3153,
3172,
3178,
3179,
3241,
3242,
3326,
3394,
3395,
3460,
3528,
3588,
3589,
3608,
3611,
3661,
3667,
3668,
3700,
3701,
3793,
3794,
3821,
3822,
3852,
3853,
3952,
3953,
3981,
3982,
4039,
4040,
4152,
4153,
4184,
4212,
4215,
4266,
4333,
4337,
4346,
4387,
4390,
4403,
4409,
4410,
4462,
4463,
4567,
4594,
4597,
4599,
4644,
4760,
4798,
4866,
4870,
4912,
4946,
4950,
4953,
4954,
4968,
4969,
4999,
5017
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 5017,
"ccnet_original_nlines": 153,
"rps_doc_curly_bracket": 0.007175600156188011,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.22747252881526947,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.007692310027778149,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.30000001192092896,
"rps_doc_frac_unique_words": 0.460132896900177,
"rps_doc_mean_word_length": 5.973422050476074,
"rps_doc_num_sentences": 64,
"rps_doc_symbol_to_word_ratio": 0.0010988999856635928,
"rps_doc_unigram_entropy": 5.181837558746338,
"rps_doc_word_count": 602,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.04783092066645622,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.05839822068810463,
"rps_doc_frac_chars_top_3gram": 0.011123470030725002,
"rps_doc_frac_chars_top_4gram": 0.007230259943753481,
"rps_doc_books_importance": -484.1597900390625,
"rps_doc_books_importance_length_correction": -484.1597900390625,
"rps_doc_openwebtext_importance": -282.0634765625,
"rps_doc_openwebtext_importance_length_correction": -282.0634765625,
"rps_doc_wikipedia_importance": -197.79525756835938,
"rps_doc_wikipedia_importance_length_correction": -197.79525756835938
},
"fasttext": {
"dclm": 0.3100360035896301,
"english": 0.6129421591758728,
"fineweb_edu_approx": 2.3937408924102783,
"eai_general_math": 0.09676337242126465,
"eai_open_web_math": 0.06096065044403076,
"eai_web_code": 0.8177854418754578
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "-1",
"labels": {
"level_1": "",
"level_2": "",
"level_3": ""
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "4",
"label": "Missing Images or Figures"
}
},
"document_type_v2": {
"primary": {
"code": "23",
"label": "Tutorial"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
6,146,135,555,062,964,000
|
Oracle FAQ Your Portal to the Oracle Knowledge Grid
HOME | ASK QUESTION | ADD INFO | SEARCH | E-MAIL US
Home -> Community -> Usenet -> comp.databases.theory -> Re: SQL Humor
Re: SQL Humor
From: paul c <toledobythesea_at_oohay.ac>
Date: Fri, 19 Aug 2005 22:35:10 GMT
Message-ID: <y8tNe.263839$5V4.254245@pd7tw3no>
Gene Wirchenko wrote:
> On Fri, 19 Aug 2005 22:37:45 +0200, Tom Ivar Helbekkmo
> <tih_at_hamartun.priv.no> wrote:
>
> [snip]
>
>
>>Of course, the member number has no physical reality, and it will be
>>an automatically assigned serial number (without reuse of defunct
>>numbers when people quit or die) -- generally, it seems to be what you
>>rant against.
>
>
> No, it is when the number is referring to how the data is
> physically stored. If the number is a record number or an address or
> other such, then it ties your data to the physical implementation. A
> member number (if used just as that) would not do that.
> ...
i don't believe that som physical connection ensues by a machine's choice of key, but maybe it doesn't matter as i'm stupid which some of my postings prove. once the value of the number is in a relation, if we are talking about relations and not something else, and we agree, if we may, to call it a 'key', then i'd say it is pretty much immutable, until somebody 'deletes' it. sorry for all the conditions, but my limited understanding requires me to specify limits!
cheers,
p Received on Fri Aug 19 2005 - 17:35:10 CDT
Original text of this message
HOME | ASK QUESTION | ADD INFO | SEARCH | E-MAIL US
|
{
"url": "http://www.orafaq.com/usenet/comp.databases.theory/2005/08/19/0527.htm",
"source_domain": "www.orafaq.com",
"snapshot_id": "crawl=CC-MAIN-2016-22",
"warc_metadata": {
"Content-Length": "7644",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:4RUGSCJK2MW3MZVGEIGKLEFPAY62WBES",
"WARC-Concurrent-To": "<urn:uuid:7448c145-bcfc-4917-ba82-47bb5fc1bc51>",
"WARC-Date": "2016-05-26T21:11:24Z",
"WARC-IP-Address": "85.25.155.19",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:WZWOXLP5MB23HILGS7S6XXCW6IQRPS7N",
"WARC-Record-ID": "<urn:uuid:fb723b92-31f8-4020-91c7-7c28d54aa113>",
"WARC-Target-URI": "http://www.orafaq.com/usenet/comp.databases.theory/2005/08/19/0527.htm",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:6faaf6eb-cd8e-42ea-a370-fa3e2a909caf>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-185-217-139.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2016-22\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web for May 2016\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
52,
104,
106,
107,
177,
178,
192,
193,
235,
271,
318,
319,
320,
342,
399,
434,
436,
445,
447,
449,
450,
521,
589,
662,
678,
679,
681,
683,
743,
814,
885,
943,
949,
950,
1418,
1419,
1427,
1472,
1473,
1503,
1504
],
"line_end_idx": [
52,
104,
106,
107,
177,
178,
192,
193,
235,
271,
318,
319,
320,
342,
399,
434,
436,
445,
447,
449,
450,
521,
589,
662,
678,
679,
681,
683,
743,
814,
885,
943,
949,
950,
1418,
1419,
1427,
1472,
1473,
1503,
1504,
1555
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 1555,
"ccnet_original_nlines": 41,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3226666748523712,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.06933332979679108,
"rps_doc_frac_lines_end_with_ellipsis": 0.02380952052772045,
"rps_doc_frac_no_alph_words": 0.3199999928474426,
"rps_doc_frac_unique_words": 0.6439999938011169,
"rps_doc_mean_word_length": 4.5879998207092285,
"rps_doc_num_sentences": 15,
"rps_doc_symbol_to_word_ratio": 0.002666669897735119,
"rps_doc_unigram_entropy": 4.8619489669799805,
"rps_doc_word_count": 250,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.061028771102428436,
"rps_doc_frac_chars_dupe_6grams": 0.061028771102428436,
"rps_doc_frac_chars_dupe_7grams": 0.061028771102428436,
"rps_doc_frac_chars_dupe_8grams": 0.061028771102428436,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.023539669811725616,
"rps_doc_frac_chars_top_3gram": 0.02877070941030979,
"rps_doc_frac_chars_top_4gram": 0.03138621896505356,
"rps_doc_books_importance": -157.906494140625,
"rps_doc_books_importance_length_correction": -145.5921173095703,
"rps_doc_openwebtext_importance": -74.8105239868164,
"rps_doc_openwebtext_importance_length_correction": -74.8105239868164,
"rps_doc_wikipedia_importance": -56.12242126464844,
"rps_doc_wikipedia_importance_length_correction": -42.470577239990234
},
"fasttext": {
"dclm": 0.07823026180267334,
"english": 0.8711337447166443,
"fineweb_edu_approx": 1.8820146322250366,
"eai_general_math": 0.0909353494644165,
"eai_open_web_math": 0.37471288442611694,
"eai_web_code": 0.0016969999996945262
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.74",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "4",
"label": "Analyze"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "1",
"label": "Truncated Snippets"
},
"secondary": {
"code": "0",
"label": "No missing content"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "5",
"label": "Comment Section"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
1,382,069,658,366,257,700
|
CSS ul li 水平對齊居中
使用 Flex
HTML
<ul>
<li>news</li>
<li>about</li>
<li>service</li>
<li>product</li>
<li>contact</li>
</ul>
CSS
<style>
ul,li{
list-style: none;
padding: 0;
}
li{
padding: .5em 1em;
margin: .5em
background-color: rgb(209, 209, 209);
}
ul{
width: 50vw;
background-color: rgb(233, 233, 233);
margin: 1em auto;
display: flex;
justify-content: center;
}
</style>
Example
See the Pen CSS ul li Horizontal center – flex by VECTOR.cool 威得數位 (@ann71727) on CodePen.
https://wcc723.github.io/css/2017/07/21/css-flex/
如果文章對您很有幫助
請我喝杯咖啡吧
Bitcoin 比特幣錢包:
18fCwNnEJ7UfMNS3GcUczPNa72NMsWcvaU
ann71727
READ CSS RWD 響應式 @media 及常用尺寸速查
發佈留言
發佈留言必須填寫的電子郵件地址不會公開。 必填欄位標示為 *
這個網站採用 Akismet 服務減少垃圾留言。進一步瞭解 Akismet 如何處理網站訪客的留言資料
|
{
"url": "https://vector.cool/css-ul-li-horizontal-align-center/",
"source_domain": "vector.cool",
"snapshot_id": "crawl=CC-MAIN-2020-34",
"warc_metadata": {
"Content-Length": "64884",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:VXKII724OAEXLSIHYNKE2ECPTCMTVDXM",
"WARC-Concurrent-To": "<urn:uuid:5591309c-289a-4b49-a276-59c3ea61ac96>",
"WARC-Date": "2020-08-04T10:31:05Z",
"WARC-IP-Address": "13.113.154.215",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:7IQPLINCXLGABMRIUTFXHIUKOUHR6PQ5",
"WARC-Record-ID": "<urn:uuid:fe3b8f4b-db10-4800-ae50-7fab938084d1>",
"WARC-Target-URI": "https://vector.cool/css-ul-li-horizontal-align-center/",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:5f4f7c73-3278-40f7-80ca-75805b66998d>"
},
"warc_info": "isPartOf: CC-MAIN-2020-34\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for August 2020\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-213.ec2.internal\r\nsoftware: Apache Nutch 1.17 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.2-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
17,
18,
26,
27,
32,
33,
38,
54,
71,
90,
109,
128,
134,
135,
139,
140,
148,
159,
185,
205,
211,
219,
246,
267,
313,
319,
327,
348,
394,
420,
443,
476,
482,
491,
492,
500,
501,
592,
593,
643,
644,
655,
663,
664,
679,
680,
715,
716,
717,
718,
727,
728,
761,
762,
767,
768,
799,
800
],
"line_end_idx": [
17,
18,
26,
27,
32,
33,
38,
54,
71,
90,
109,
128,
134,
135,
139,
140,
148,
159,
185,
205,
211,
219,
246,
267,
313,
319,
327,
348,
394,
420,
443,
476,
482,
491,
492,
500,
501,
592,
593,
643,
644,
655,
663,
664,
679,
680,
715,
716,
717,
718,
727,
728,
761,
762,
767,
768,
799,
800,
851
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 851,
"ccnet_original_nlines": 58,
"rps_doc_curly_bracket": 0.007050530053675175,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.025380710139870644,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.04060913994908333,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.5634517669677734,
"rps_doc_frac_unique_words": 0.738095223903656,
"rps_doc_mean_word_length": 6.392857074737549,
"rps_doc_num_sentences": 7,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.0089921951293945,
"rps_doc_word_count": 84,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.01862196996808052,
"rps_doc_frac_chars_top_3gram": 0.026070760563015938,
"rps_doc_frac_chars_top_4gram": 0,
"rps_doc_books_importance": -96.06121063232422,
"rps_doc_books_importance_length_correction": -96.06121063232422,
"rps_doc_openwebtext_importance": -61.02301025390625,
"rps_doc_openwebtext_importance_length_correction": -58.05677795410156,
"rps_doc_wikipedia_importance": -31.315410614013672,
"rps_doc_wikipedia_importance_length_correction": -31.315410614013672
},
"fasttext": {
"dclm": 0.8824237585067749,
"english": 0.02528250962495804,
"fineweb_edu_approx": 1.7157303094863892,
"eai_general_math": 0.002850289922207594,
"eai_open_web_math": 0.02251744084060192,
"eai_web_code": 0.8177684545516968
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "-1",
"labels": {
"level_1": "",
"level_2": "",
"level_3": ""
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "4",
"label": "Missing Images or Figures"
}
},
"document_type_v2": {
"primary": {
"code": "23",
"label": "Tutorial"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "1",
"label": "No Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "1",
"label": "General Audience"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-2,185,724,131,701,317,000
|
Take the 2-minute tour ×
Stack Overflow is a question and answer site for professional and enthusiast programmers. It's 100% free, no registration required.
I am new to Database interection with C#, I am trying to writing 10000 records in database in a loop with the help of SqlCommand and SqlConnection objects with the help of SqlTransaction and committing after 5000. It is taking 10 seconds to processed.
SqlConnection myConnection = new SqlConnection("..Connection String..");
myConnection.Open();
SqlCommand myCommand = new SqlCommand();
myCommand.CommandText = "exec StoredProcedureInsertOneRowInTable Param1, Param2........";
myCommand.Connection = myConnection;
SqlTransaction myTrans = myConnection.Begintransaction();
for(int i=0;i<10000;i++)
{
mycommand.ExecuteNonQuery();
if(i%5000==0)
{
myTrans.commit();
myTrans = myConnection.BeginTransaction();
mycommand.Transaction = myTrans;
}
}
Above code is giving me only 1000 rows write/sec in database.
But when i tried to implement same logic in SQL and execute it on Database with SqlManagement Studio the it gave me 10000 write/sec. When I compare the behaviour of above two approch then it showes me that while executing with ADO.Net there is large number of Logical reads.
my questions are: 1. Why there is logical reads in ADO.Net execution? 2. Is tansaction have some hand shaking? 3. Why they are not available in case of management studio? 4. If I want very fast insert transactions on DB then what will be the approach? .
Updated Information about Database objects
Table: tbl_FastInsertTest No Primary Key, Only 5 fields first three are type of int (F1,F2,F3) and last 2(F4,F5) are type varchar(30)
storedprocedure:
create proc stp_FastInsertTest
{
@nF1 int,
@nF2 int,
@nF3 int,
@sF4 varchar(30),
@sF5 varchar(30)
}
as
Begin
set NoCOUNT on
Insert into tbl_FastInsertTest
{
[F1],
[F2],
[F3],
[F4],
[F5]
}
Values
{
@nF1,
@nF2,
@nF3,
@sF4,
@sF5,
} end
--------------------------------------------------------------------------------------
SQL Block Executing on SSMS
--When I am executing following code on SSMS then it is giving me more than 10000 writes per second but when i tried to execute same STP on ADO than it gave me 1000 to 1200 writes per second
--while reading no locks
begin trans
declare @i int
set @i=0
While(1<>0)
begin
exec stp_FastInsertTest 1,2,3,'vikram','varma'
set @i=@i+1
if(@i=5000)
begin
commit trans
set @i=0
begin trans
end
end
share|improve this question
3 Answers 3
If you are running something like:
exec StoredProcedureInsertOneRowInTable 'blah', ...
exec StoredProcedureInsertOneRowInTable 'bloop', ...
exec StoredProcedureInsertOneRowInTable 'more', ...
in SSMS, that is an entirely different scenario, where all of that is a single batch. With ADO.NET you are paying a round-trip per ExecuteNonQuery - I'm actually impressed it managed 1000/s.
Re the logical reads, that could just be looking at the query-plan cache, but without knowing more about StoredProcedureInsertOneRowInTable it is impossible to comment on whether something query-specific is afoot. But I suspect you have some different SET conditions between SSMS and ADO.NET that is forcing it to use a different plan - this is in particular a problem with things like persisted calculated indexed columns, and columns "promoted" out of a sql-xml field.
Re making it faster - in this case it sounds like a table-valued parameters is exactly the thing, but you should also review the other options here
share|improve this answer
Thanks A lot, To all of you to give your precious Time. And sorry I haven't Add sufficiant information I have Updated the details. – vikram Feb 3 '11 at 9:25
@vikram I see no update... – Marc Gravell Feb 3 '11 at 9:26
How can I identify that my code (Given in Question) is executing as a batch, as in first seen it seems to be executed on SSMS itself. – vikram Feb 3 '11 at 10:16
@vikram - simply : it isn't; you are making 10000 calls to ExecuteNonQuery; each of those is a round-trip, so has latency. Is it the moral equivalent of running each line via SSMS separately - i.e. select line 1, execute, select line 2, execute, select line 3, execute... – Marc Gravell Feb 3 '11 at 10:39
• For performant inserts take a look at SqlBulkCopy class if it works for you it should be fast.
• As Sean said, using parameterized queries is always a good idea.
• Using a StringBuilder class, batching thousand INSERT statements in a single query and committing the transaction is a proven way of inserting data:
var sb=new StringBuilder();
for(int i=0;i < 1000;i++)
{
sb.AppendFormat("INSERT INTO Table(col1,col2)
VALUES({0},{1});",values1[i],values2[i]); }
sqlCommand.Text=sb.ToString();
• Your code doesn't look right to me, you are not committing transactions at each batch. Your code keeps opening new transactions.
• It is always a good practice to drop indexes while inserting a lot of data, and adding them later. Indexes will slow down your writes.
• Sql Management Studio does not have transactions but Sql has, try this:
BEGIN TRANSACTION MyTransaction
INSERT INTO Table(Col1,Col1) VALUES(Val10,Val20);
INSERT INTO Table(Col1,Col1) VALUES(Val11,Val21);
INSERT INTO Table(Col1,Col1) VALUES(Val12,Val23);
COMMIT TRANSACTION
share|improve this answer
Thanks A lot, for your precious Time. And sorry I haven't Add sufficiant information I have Updated the details. – vikram Feb 3 '11 at 9:28
I understand that the way I am doing insert in DB is not in good practice but my requirement is to handle large amount of real time data (9000 per sec) and stored in Data base. and I can't do bulk insert as i want to write in DB as it received, As some other application may want it by reading with "no lock". Also SSMS have transaction as I have given the sample i am executing on SSMS – vikram Feb 3 '11 at 10:14
You need to use a parameterized query so that the execution path can get processed and cached. Since you're using string concatenation (shudder, this is bad, google sql injection) to build the query, SQL Server treats those 10,000 queries are separate, individual queries and builds an execution plan for each one.
MSDN: http://msdn.microsoft.com/en-us/library/yy6y35y8.aspx although you're going to want to simplify their code a bit and you'll have to reset the parameters on the command.
If you really, really want to get the data in the db fast, think about using bcp... but you better make sure the data is clean first (as there's no real error checking/handling on it.
share|improve this answer
Thanks A lot, for your precious Time. And sorry I haven't Add sufficiant information I have Updated the details. – vikram Feb 3 '11 at 9:23
Perametarized query is no doubt is good choice but I am comparing two situtations one at ADO and another at SSMS. – vikram Feb 3 '11 at 10:17
Your Answer
discard
By posting your answer, you agree to the privacy policy and terms of service.
Not the answer you're looking for? Browse other questions tagged or ask your own question.
|
{
"url": "http://stackoverflow.com/questions/4859627/sql-transaction-with-ado-net",
"source_domain": "stackoverflow.com",
"snapshot_id": "crawl=CC-MAIN-2014-49",
"warc_metadata": {
"Content-Length": "88823",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:STRQ2NDBS43U5TWFIUNFJ4IDOTOGEP6Z",
"WARC-Concurrent-To": "<urn:uuid:58595889-b7aa-4fe4-aa11-0b13c9b5b878>",
"WARC-Date": "2014-11-26T14:11:06Z",
"WARC-IP-Address": "198.252.206.16",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:Y2AT3ZJIQXZMOVNC62VW4D4IWHSBAPCC",
"WARC-Record-ID": "<urn:uuid:fb037aca-3879-44d4-a871-c1ef07d53117>",
"WARC-Target-URI": "http://stackoverflow.com/questions/4859627/sql-transaction-with-ado-net",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:1268d66b-7b00-4cfc-81b1-63f2609453ca>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-235-23-156.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2014-49\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web with URLs provided by Blekko for November 2014\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
25,
157,
158,
410,
411,
484,
505,
546,
636,
673,
731,
756,
758,
788,
803,
805,
825,
870,
903,
905,
907,
908,
970,
971,
1246,
1247,
1501,
1502,
1545,
1546,
1680,
1681,
1698,
1699,
1731,
1734,
1744,
1755,
1766,
1785,
1804,
1807,
1813,
1820,
1836,
1874,
1883,
1898,
1913,
1928,
1943,
1957,
1966,
1980,
1989,
2004,
2019,
2034,
2049,
2064,
2077,
2165,
2166,
2194,
2195,
2386,
2387,
2412,
2413,
2426,
2442,
2451,
2452,
2465,
2473,
2523,
2537,
2538,
2554,
2566,
2585,
2597,
2612,
2618,
2619,
2624,
2652,
2653,
2665,
2666,
2701,
2702,
2754,
2807,
2859,
2860,
3051,
3052,
3523,
3524,
3672,
3673,
3699,
3704,
3863,
3868,
3929,
3934,
4097,
4102,
4409,
4508,
4577,
4730,
4731,
4763,
4764,
4794,
4801,
4853,
4858,
4859,
4907,
4908,
4943,
4948,
5081,
5082,
5221,
5297,
5330,
5384,
5438,
5492,
5515,
5541,
5546,
5687,
5692,
6108,
6109,
6424,
6425,
6600,
6601,
6785,
6786,
6812,
6817,
6958,
6963,
7106,
7107,
7119,
7120,
7122,
7130,
7131,
7209,
7210
],
"line_end_idx": [
25,
157,
158,
410,
411,
484,
505,
546,
636,
673,
731,
756,
758,
788,
803,
805,
825,
870,
903,
905,
907,
908,
970,
971,
1246,
1247,
1501,
1502,
1545,
1546,
1680,
1681,
1698,
1699,
1731,
1734,
1744,
1755,
1766,
1785,
1804,
1807,
1813,
1820,
1836,
1874,
1883,
1898,
1913,
1928,
1943,
1957,
1966,
1980,
1989,
2004,
2019,
2034,
2049,
2064,
2077,
2165,
2166,
2194,
2195,
2386,
2387,
2412,
2413,
2426,
2442,
2451,
2452,
2465,
2473,
2523,
2537,
2538,
2554,
2566,
2585,
2597,
2612,
2618,
2619,
2624,
2652,
2653,
2665,
2666,
2701,
2702,
2754,
2807,
2859,
2860,
3051,
3052,
3523,
3524,
3672,
3673,
3699,
3704,
3863,
3868,
3929,
3934,
4097,
4102,
4409,
4508,
4577,
4730,
4731,
4763,
4764,
4794,
4801,
4853,
4858,
4859,
4907,
4908,
4943,
4948,
5081,
5082,
5221,
5297,
5330,
5384,
5438,
5492,
5515,
5541,
5546,
5687,
5692,
6108,
6109,
6424,
6425,
6600,
6601,
6785,
6786,
6812,
6817,
6958,
6963,
7106,
7107,
7119,
7120,
7122,
7130,
7131,
7209,
7210,
7300
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 7300,
"ccnet_original_nlines": 160,
"rps_doc_curly_bracket": 0.002191779902204871,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.32304662466049194,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.05055810883641243,
"rps_doc_frac_lines_end_with_ellipsis": 0.018633540719747543,
"rps_doc_frac_no_alph_words": 0.27774131298065186,
"rps_doc_frac_unique_words": 0.40947073698043823,
"rps_doc_mean_word_length": 4.969359397888184,
"rps_doc_num_sentences": 72,
"rps_doc_symbol_to_word_ratio": 0.005909389816224575,
"rps_doc_unigram_entropy": 5.586727619171143,
"rps_doc_word_count": 1077,
"rps_doc_frac_chars_dupe_10grams": 0.06464873254299164,
"rps_doc_frac_chars_dupe_5grams": 0.09360986948013306,
"rps_doc_frac_chars_dupe_6grams": 0.08800447732210159,
"rps_doc_frac_chars_dupe_7grams": 0.07922271639108658,
"rps_doc_frac_chars_dupe_8grams": 0.06464873254299164,
"rps_doc_frac_chars_dupe_9grams": 0.06464873254299164,
"rps_doc_frac_chars_top_2gram": 0.005979069974273443,
"rps_doc_frac_chars_top_3gram": 0.008968610316514969,
"rps_doc_frac_chars_top_4gram": 0.011958150193095207,
"rps_doc_books_importance": -617.6412353515625,
"rps_doc_books_importance_length_correction": -617.6412353515625,
"rps_doc_openwebtext_importance": -389.8700866699219,
"rps_doc_openwebtext_importance_length_correction": -389.8700866699219,
"rps_doc_wikipedia_importance": -232.35781860351562,
"rps_doc_wikipedia_importance_length_correction": -232.35781860351562
},
"fasttext": {
"dclm": 0.05235737934708595,
"english": 0.8617280721664429,
"fineweb_edu_approx": 1.349522590637207,
"eai_general_math": 0.04375255107879639,
"eai_open_web_math": 0.22803586721420288,
"eai_web_code": 0.01594335027039051
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.44",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "4",
"label": "Analyze"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "1",
"label": "Leftover HTML"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "4",
"label": "Graduate/Expert Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-3,545,786,857,306,666,500
|
The Vonage AI Studio: A Sample Integration with SimplyDoc
Users today expect seamless, omnichannel communication across their devices. This is the promise of Unified Communications. UC allows a user to switch not only from computer to tablet to mobile within a single session, but also from one mode of communication (voice, video, messaging, etc.) to another. Live video, our speciality here at WebRTC.ventures, is an important component of the UC suite. But it is just one tool in a large toolbox. As we build WebRTC applications, we also consider where telephony-based tools like SMS messaging and Voice would further enhance UX to offer a true omnichannel experience.
Vonage is a major Communication Platform As a Service (CPaaS) provider which offers an array of communications libraries including Video, SMS, Voice, Chat and more. As you can imagine, integrating all of these experiences is no small task. Vonage’s AI Studio meets this challenge. It offers a very compelling way to combine these services into a single workflow that also includes Voice Recognition, as well as the ability to integrate custom API calls of your own.
Vonage AI Studio + SimplyDoc Telehealth
To demonstrate this functionality, we have built a simple integration of the Vonage AI Studio with our SimplyDoc Telehealth Application Starter Kit. SimplyDoc was born out of our experience developing custom telehealth applications. The idea of this codebase, which is built on top of the Vonage APIs, is that the majority of the telehealth clients that came to us needed a similar base level of functionality:
1. Video telehealth visits
2. Phone integration as a backup
3. Text chat
4. Screen sharing
5. Secure file transfer
We license the SimplyDoc code to telehealth entrepreneurs to get their applications to market faster than a custom app. Generally speaking, this usually ends up being an “80% solution.” The remaining 20% is what makes that client’s telehealth application unique in the marketplace. Perhaps they add in a special type of image processing, integration with other apps, or a custom workflow. Whatever it is, that is their special sauce as a healthcare provider and we can build that for them around the SimplyDoc codebase.
In this blog post, we’ll show you how the Vonage AI Studio allows a patient to reschedule their telehealth visit via a phone call. This simple example could be extended to include other communications channels such as SMS messaging, text chat with a chatbot, or even WhatsApp messaging.
The Experiment
Scheduling an appointment is a vital component of the telehealth process. Telehealth visits can be scheduled online by the patient in SimplyDoc’s base functionality. If they want to later change the appointment? No problem! Our standard configuration allows this to be done via the website.
For the sake of experimentation, we wanted to see how the Vonage AI Studio would allow the rescheduling via a phone call with a bot instead. Ricardo, a member of our WebRTC.ventures development team, recorded a complete demo of how the integration works and the configuration process. In the rest of this blog post, I will walk you through the key parts. You can also watch the full video of the “Vonage AI Studio Walkthrough” here.
Reschedule Flow
In the Vonage AI Studio, you start out by setting up an Agent, which is the phone number and/or chatbot that you are working with. Each agent can have multiple workflows associated with it. In our sample, SimplyDoc Agent we will be working with a flow that we have named “Reschedule Flow.” As the name indicates, this flow is for when a patient calls into a phone number to reschedule their appointment. The workflow dashboard looks similar to the following:
Our Rescheduling Flow on the Vonage AI Studio dashboard.
When the patient calls the phone number associated with the Agent, they are first directed to the Main Flow. This is not pictured above, but you can see in Ricardo’s video that it creates a set of action items for the patient to choose. When the patient says something like “I want to reschedule my appointment,” they are redirected to the Reschedule Flow shown above.
Note that in our demo video and in this blog post, I’m referring to all the patient actions as if they are done over a phone call. However, one of the nice things about the Vonage AI Studio is that the same workflow can also be used with chatbots who are interacting with the patient over SMS messaging, WhatsApp messages, or a text chat in a browser. With one workflow, you can set up multiple channels for your users to communicate with you, depending on their personal preferences or the device they are using at that time. All the complexity is handled for you by the AI Studio!
Testing and Publishing
To take your application live, you Publish it in the Vonage AI Studio. That’s what will tie it to your real phone number for the Agent. While you’re developing and testing your flows, it works a little differently. In Test Mode, you can enter your own personal phone number. The AI Studio will call out to you instead of you dialing into a production phone number. This allows developers to test their workflows from their personal phones, as Ricardo shows in this portion of the video.
Setting your phone number in AI Studio for testing purposes. (Phone number hidden.)
Alternatively, you can do your testing via text chat with a bot directly in the AI Studio. This will work the same way as on your phone as well as simulating what this flow would look like if implemented over any of the text-based channels like SMS, WhatsApp, or your own custom text bot on your website.
Integrating Vonage AI Studio With Your Custom App
The next part of Ricardo’s video shows how you integrate the AI Studio with your own custom applications. In order to reschedule a patient’s appointment, we need to identify their original appointment in our database. There are a number of ways you might implement this in a real application. Perhaps you ask the patient to enter their birthdate, type in their name, or you try to identify the patient based on the phone number they are calling from. For the purposes of keeping our demo simple, we assume the patient knows a unique identifier for their appointment. This Appointment ID has been supplied to them in the email confirmation for their appointment.
In this next portion of the video, you can listen as Ricardo receives a test call from the AI Studio, and the bot voice asks him for his Appointment ID. After that, Ricardo then tells the bot the new date and time that he wants to schedule the appointment.
When a patient supplies a piece of data such as the Appointment ID, Ricardo must configure the workflow to supply that data to our custom application. The Collect blocks will gather that information from the user and pass them as a Parameter to subsequent blocks in Ricardo’s workflow. Then he can put in data blocks that validate that the information supplied by the user is of the correct type (a number or a date for example). Finally, he configures a WebHook block to send that Parameter’s data to our custom APIs in SimplyDoc. Using that WebHook, our SimplyDoc code can receive and validate that Appointment ID, as well as change the appointment to the new date in our database.
In this example, our API then returns a boolean indicating Success or Failure of the date change. The bot can then notify the patient and conclude the call.
When the system doesn’t quite understand Ricardo’s reading of his Appointment ID, you can see that it can ask him to type it in using the keys on his phone. This will generate DTMF tones, just like a typical call center application.
The second and longer part of Ricardo’s video does a complete walkthrough of the workflow and how he configures everything. I’ll point to two particularly interesting aspects here.
Configuring WebHooks
First, if you want to see how the WebHooks are configured, start at around minute 23:00 in the video. As Ricardo discusses and as shown in the screenshot below, you will enter a URL to your API and supply the parameters given by the user as part of that URL. Then you can define the returned data from the API and assign them to variables so that they can be used later in the workflow.
Example of a WebHook call from Vonage AI Studio.
Voice Recognition
Second, it’s also interesting to see how the voice recognition aspect of the AI Studio works. Whenever our patient is going to talk to the bot, that is called an Intention. The Intention indicates the “intent” of why the patient is speaking to the bot. For example, in the screenshot below, the patient is answering the first question of the phone call, where the bot asks the patient what they want to do. Our bot has been configured to allow multiple intents, such as switching their telehealth visit from a video call to a phone call.
Example intents in our Vonage AI Studio integration with SimplyDoc.
Rescheduling the telehealth visit is one of those intents, and the one we’ve been focusing on in this blog post. So, we need to “train” the bot to understand what our patient might say when they want to reschedule an appointment. Ricardo has configured that in the screenshot below by entering in typical phrases that a patient might say, such as “I need to reschedule my appointment.” The Vonage AI studio converts the patient’s speech to text. This allows the AI to intelligently match that text to one of the Intents that has been configured.
Example training set phrases in our “Reschedule appointment” intent.
The more phrases Ricardo puts into the training set for this Intent, the more accurately we can capture what the patient wants to do. To see more on the Intents, skip to around minute 13:00 of the video.
Other Applications
In this blog post and in Ricardo’s more detailed video, we have given you a taste of how powerful the Vonage AI Studio can be. We integrated a simple rescheduling workflow into our custom telehealth application and in the process opened up a completely new channel of communication with our application! All with relatively few coding changes.
We’ve kept this example simple intentionally. There’s actually a lot more we could do with it. For example, since we know who the patient is and their phone number, we could use Vonage to text them confirmation of the appointment change. This integration with SMS messaging could be built into the same workflow for rescheduling our appointment, so no code would need to be built directly in our SimplyDoc application.
We could also add in other typical call center flows like transferring to a human if the user presses “Zero”. This action could cause the AI Studio to exit the standard workflow at any point and initiate a call to the receptionist at our doctor’s office.
Not Just for Telehealth: Call Centers and More
Although we’ve focused on a telehealth application here, the same concepts can be applied to any application. You can configure just about anything you would expect a typical call center application to do and tie it into your custom application with the AI Studio.
This opens up a lot of possibilities for customer contact centers to improve the service they provide to their customers, and to automate many of the functions that a customer needs.
When you come to WebRTC.ventures and ask us to build a live video application, one of the first questions we will ask is if you want to use one of the CPaaS solutions like Vonage. A major benefit of using a CPaaS is the ability to leverage the enterprise capabilities already built into that CPaaS. This speeds your time to market and reduces the cost of building your application. The Vonage AI Studio is a powerful tool to consider if you would like to add omnichannel and Unified Communications capabilities into your live video application.
Are you looking to build a custom video application and integrate it with telephony and call center functionality? Leverage our expertise in the Vonage APIs, and contact our team today!
©[current-year] KLEO Template a premium and multipurpose theme from Seventh Queen
Log in with your credentials
Forgot your details?
|
{
"url": "http://www.webrtc.ventures/2022/04/the-vonage-ai-studio-telehealth-integration/",
"source_domain": "www.webrtc.ventures",
"snapshot_id": "crawl=CC-MAIN-2022-49",
"warc_metadata": {
"Content-Length": "109630",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:QRSXZWKHDRIHUX2XQ2KXAPPQOIUT6KBY",
"WARC-Concurrent-To": "<urn:uuid:731c081f-e9d5-4c28-8c06-34b9c4935226>",
"WARC-Date": "2022-11-27T16:32:01Z",
"WARC-IP-Address": "162.240.66.254",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:JBZQUFJZHN2WCO23RVW4F5XWVO3CPFR4",
"WARC-Record-ID": "<urn:uuid:64c9572e-d5d3-4e8f-9bcf-f44d712243a1>",
"WARC-Target-URI": "http://www.webrtc.ventures/2022/04/the-vonage-ai-studio-telehealth-integration/",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:6a3e9664-d60f-4059-85ec-972fa590faae>"
},
"warc_info": "isPartOf: CC-MAIN-2022-49\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for November/December 2022\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-150\r\nsoftware: Apache Nutch 1.19 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.4-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
58,
59,
673,
674,
1140,
1141,
1182,
1183,
1594,
1595,
1624,
1659,
1674,
1694,
1721,
1722,
2242,
2243,
2530,
2531,
2546,
2547,
2838,
2839,
3272,
3273,
3289,
3290,
3749,
3750,
3807,
3808,
4177,
4178,
4761,
4762,
4785,
4786,
5273,
5274,
5358,
5359,
5664,
5665,
5715,
5716,
6378,
6379,
6636,
6637,
7321,
7322,
7479,
7480,
7713,
7714,
7895,
7896,
7917,
7918,
8305,
8306,
8355,
8356,
8374,
8375,
8915,
8916,
8984,
8985,
9531,
9532,
9601,
9602,
9806,
9807,
9826,
9827,
10171,
10172,
10591,
10592,
10847,
10848,
10895,
10896,
11161,
11162,
11347,
11348,
11893,
11894,
12080,
12081,
12163,
12164,
12193,
12194
],
"line_end_idx": [
58,
59,
673,
674,
1140,
1141,
1182,
1183,
1594,
1595,
1624,
1659,
1674,
1694,
1721,
1722,
2242,
2243,
2530,
2531,
2546,
2547,
2838,
2839,
3272,
3273,
3289,
3290,
3749,
3750,
3807,
3808,
4177,
4178,
4761,
4762,
4785,
4786,
5273,
5274,
5358,
5359,
5664,
5665,
5715,
5716,
6378,
6379,
6636,
6637,
7321,
7322,
7479,
7480,
7713,
7714,
7895,
7896,
7917,
7918,
8305,
8306,
8355,
8356,
8374,
8375,
8915,
8916,
8984,
8985,
9531,
9532,
9601,
9602,
9806,
9807,
9826,
9827,
10171,
10172,
10591,
10592,
10847,
10848,
10895,
10896,
11161,
11162,
11347,
11348,
11893,
11894,
12080,
12081,
12163,
12164,
12193,
12194,
12214
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 12214,
"ccnet_original_nlines": 98,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.4551607370376587,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.023688659071922302,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.11252114921808243,
"rps_doc_frac_unique_words": 0.2774566411972046,
"rps_doc_mean_word_length": 4.746628284454346,
"rps_doc_num_sentences": 115,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 5.417533874511719,
"rps_doc_word_count": 2076,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.017657799646258354,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.021108180284500122,
"rps_doc_frac_chars_top_3gram": 0.021311139687895775,
"rps_doc_frac_chars_top_4gram": 0.018977070227265358,
"rps_doc_books_importance": -1111.1151123046875,
"rps_doc_books_importance_length_correction": -1111.1151123046875,
"rps_doc_openwebtext_importance": -728.779052734375,
"rps_doc_openwebtext_importance_length_correction": -728.779052734375,
"rps_doc_wikipedia_importance": -474.4212951660156,
"rps_doc_wikipedia_importance_length_correction": -474.4212951660156
},
"fasttext": {
"dclm": 0.25500625371932983,
"english": 0.9386262893676758,
"fineweb_edu_approx": 1.7473788261413574,
"eai_general_math": 0.19901514053344727,
"eai_open_web_math": 0.13761693239212036,
"eai_web_code": 0.331207275390625
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.0285",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "610.285",
"labels": {
"level_1": "Industrial arts, Technology, and Engineering",
"level_2": "Medicine",
"level_3": ""
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "4",
"label": "Analyze"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "4",
"label": "Missing Images or Figures"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "23",
"label": "Tutorial"
},
"secondary": {
"code": "10",
"label": "Knowledge Article"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-4,609,277,350,368,578,000
|
HAMMER 60I/Many: Mirroring
[dragonfly.git] / sys / netinet / in_gif.c
blob0b7ce017fd5b3670b71771c5a1a45c20cd7fe408
1 /*
2 * $FreeBSD: src/sys/netinet/in_gif.c,v 1.5.2.11 2003/01/23 21:06:45 sam Exp $
3 * $DragonFly: src/sys/netinet/in_gif.c,v 1.17 2008/06/08 08:38:05 sephe Exp $
4 * $KAME: in_gif.c,v 1.54 2001/05/14 14:02:16 itojun Exp $
5 */
6 /*
7 * Copyright (C) 1995, 1996, 1997, and 1998 WIDE Project.
8 * All rights reserved.
10 * Redistribution and use in source and binary forms, with or without
11 * modification, are permitted provided that the following conditions
12 * are met:
13 * 1. Redistributions of source code must retain the above copyright
14 * notice, this list of conditions and the following disclaimer.
15 * 2. Redistributions in binary form must reproduce the above copyright
16 * notice, this list of conditions and the following disclaimer in the
17 * documentation and/or other materials provided with the distribution.
18 * 3. Neither the name of the project nor the names of its contributors
19 * may be used to endorse or promote products derived from this software
20 * without specific prior written permission.
22 * THIS SOFTWARE IS PROVIDED BY THE PROJECT AND CONTRIBUTORS ``AS IS'' AND
23 * ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
24 * IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE
25 * ARE DISCLAIMED. IN NO EVENT SHALL THE PROJECT OR CONTRIBUTORS BE LIABLE
26 * FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
27 * DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS
28 * OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION)
29 * HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT
30 * LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY
31 * OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF
32 * SUCH DAMAGE.
35 #include "opt_inet.h"
36 #include "opt_inet6.h"
38 #include <sys/param.h>
39 #include <sys/systm.h>
40 #include <sys/socket.h>
41 #include <sys/sockio.h>
42 #include <sys/mbuf.h>
43 #include <sys/errno.h>
44 #include <sys/kernel.h>
45 #include <sys/sysctl.h>
46 #include <sys/protosw.h>
48 #include <sys/malloc.h>
50 #include <machine/stdarg.h>
52 #include <net/if.h>
53 #include <net/route.h>
55 #include <netinet/in.h>
56 #include <netinet/in_systm.h>
57 #include <netinet/ip.h>
58 #include <netinet/ip_var.h>
59 #include <netinet/in_gif.h>
60 #include <netinet/in_var.h>
61 #include <netinet/ip_encap.h>
62 #include <netinet/ip_ecn.h>
64 #ifdef INET6
65 #include <netinet/ip6.h>
66 #endif
68 #include <net/gif/if_gif.h>
69 #include <net/net_osdep.h>
71 #include <sys/thread2.h> /* ipstat */
73 #ifdef INET
74 static int gif_validate4 (const struct ip *, struct gif_softc *,
75 struct ifnet *);
77 extern struct domain inetdomain;
78 const struct protosw in_gif_protosw =
79 { SOCK_RAW, &inetdomain, 0/*IPPROTO_IPV[46]*/, PR_ATOMIC|PR_ADDR,
80 in_gif_input, rip_output, 0, rip_ctloutput,
81 cpu0_soport,
82 0, 0, 0, 0,
83 &rip_usrreqs
86 int ip_gif_ttl = GIF_TTL;
87 SYSCTL_INT(_net_inet_ip, IPCTL_GIF_TTL, gifttl, CTLFLAG_RW,
88 &ip_gif_ttl, 0, "");
90 int
91 in_gif_output(struct ifnet *ifp, int family, struct mbuf *m)
93 struct gif_softc *sc = (struct gif_softc*)ifp;
94 struct sockaddr_in *dst = (struct sockaddr_in *)&sc->gif_ro.ro_dst;
95 struct sockaddr_in *sin_src = (struct sockaddr_in *)sc->gif_psrc;
96 struct sockaddr_in *sin_dst = (struct sockaddr_in *)sc->gif_pdst;
97 struct ip iphdr; /* capsule IP header, host byte ordered */
98 int proto, error;
99 u_int8_t tos;
101 if (sin_src == NULL || sin_dst == NULL ||
102 sin_src->sin_family != AF_INET ||
103 sin_dst->sin_family != AF_INET) {
104 m_freem(m);
105 return EAFNOSUPPORT;
108 switch (family) {
109 #ifdef INET
110 case AF_INET:
112 struct ip *ip;
114 proto = IPPROTO_IPV4;
115 if (m->m_len < sizeof *ip) {
116 m = m_pullup(m, sizeof *ip);
117 if (!m)
118 return ENOBUFS;
120 ip = mtod(m, struct ip *);
121 tos = ip->ip_tos;
122 break;
124 #endif
125 #ifdef INET6
126 case AF_INET6:
128 struct ip6_hdr *ip6;
129 proto = IPPROTO_IPV6;
130 if (m->m_len < sizeof *ip6) {
131 m = m_pullup(m, sizeof *ip6);
132 if (!m)
133 return ENOBUFS;
135 ip6 = mtod(m, struct ip6_hdr *);
136 tos = (ntohl(ip6->ip6_flow) >> 20) & 0xff;
137 break;
139 #endif
140 default:
141 #ifdef DEBUG
142 kprintf("in_gif_output: warning: unknown family %d passed\n",
143 family);
144 #endif
145 m_freem(m);
146 return EAFNOSUPPORT;
149 bzero(&iphdr, sizeof iphdr);
150 iphdr.ip_src = sin_src->sin_addr;
151 /* bidirectional configured tunnel mode */
152 if (sin_dst->sin_addr.s_addr != INADDR_ANY)
153 iphdr.ip_dst = sin_dst->sin_addr;
154 else {
155 m_freem(m);
156 return ENETUNREACH;
158 iphdr.ip_p = proto;
159 /* version will be set in ip_output() */
160 iphdr.ip_ttl = ip_gif_ttl;
161 iphdr.ip_len = m->m_pkthdr.len + sizeof(struct ip);
162 if (ifp->if_flags & IFF_LINK1)
163 ip_ecn_ingress(ECN_ALLOWED, &iphdr.ip_tos, &tos);
164 else
165 ip_ecn_ingress(ECN_NOCARE, &iphdr.ip_tos, &tos);
167 /* prepend new IP header */
168 M_PREPEND(m, sizeof(struct ip), MB_DONTWAIT);
169 if (m && m->m_len < sizeof(struct ip))
170 m = m_pullup(m, sizeof(struct ip));
171 if (m == NULL) {
172 kprintf("ENOBUFS in in_gif_output %d\n", __LINE__);
173 return ENOBUFS;
175 bcopy(&iphdr, mtod(m, struct ip *), sizeof(struct ip));
177 if (dst->sin_family != sin_dst->sin_family ||
178 dst->sin_addr.s_addr != sin_dst->sin_addr.s_addr) {
179 /* cache route doesn't match */
180 dst->sin_family = sin_dst->sin_family;
181 dst->sin_len = sizeof(struct sockaddr_in);
182 dst->sin_addr = sin_dst->sin_addr;
183 if (sc->gif_ro.ro_rt != NULL) {
184 RTFREE(sc->gif_ro.ro_rt);
185 sc->gif_ro.ro_rt = NULL;
187 #if 0
188 sc->gif_if.if_mtu = GIF_MTU;
189 #endif
192 if (sc->gif_ro.ro_rt == NULL) {
193 rtalloc(&sc->gif_ro);
194 if (sc->gif_ro.ro_rt == NULL) {
195 m_freem(m);
196 return ENETUNREACH;
199 /* if it constitutes infinite encapsulation, punt. */
200 if (sc->gif_ro.ro_rt->rt_ifp == ifp) {
201 m_freem(m);
202 return ENETUNREACH; /* XXX */
204 #if 0
205 ifp->if_mtu = sc->gif_ro.ro_rt->rt_ifp->if_mtu -
206 sizeof(struct ip);
207 #endif
210 error = ip_output(m, NULL, &sc->gif_ro, 0, NULL, NULL);
211 return(error);
214 void
215 in_gif_input(struct mbuf *m, ...)
217 struct ifnet *gifp = NULL;
218 struct ip *ip;
219 int af;
220 u_int8_t otos;
221 int off, proto;
222 __va_list ap;
224 __va_start(ap, m);
225 off = __va_arg(ap, int);
226 proto = __va_arg(ap, int);
227 __va_end(ap);
229 ip = mtod(m, struct ip *);
231 gifp = (struct ifnet *)encap_getarg(m);
233 if (gifp == NULL || (gifp->if_flags & IFF_UP) == 0) {
234 m_freem(m);
235 ipstat.ips_nogif++;
236 return;
239 otos = ip->ip_tos;
240 m_adj(m, off);
242 switch (proto) {
243 #ifdef INET
244 case IPPROTO_IPV4:
246 struct ip *ip;
247 af = AF_INET;
248 if (m->m_len < sizeof *ip) {
249 m = m_pullup(m, sizeof *ip);
250 if (!m)
251 return;
253 ip = mtod(m, struct ip *);
254 if (gifp->if_flags & IFF_LINK1)
255 ip_ecn_egress(ECN_ALLOWED, &otos, &ip->ip_tos);
256 else
257 ip_ecn_egress(ECN_NOCARE, &otos, &ip->ip_tos);
258 break;
260 #endif
261 #ifdef INET6
262 case IPPROTO_IPV6:
264 struct ip6_hdr *ip6;
265 u_int8_t itos;
266 af = AF_INET6;
267 if (m->m_len < sizeof *ip6) {
268 m = m_pullup(m, sizeof *ip6);
269 if (!m)
270 return;
272 ip6 = mtod(m, struct ip6_hdr *);
273 itos = (ntohl(ip6->ip6_flow) >> 20) & 0xff;
274 if (gifp->if_flags & IFF_LINK1)
275 ip_ecn_egress(ECN_ALLOWED, &otos, &itos);
276 else
277 ip_ecn_egress(ECN_NOCARE, &otos, &itos);
278 ip6->ip6_flow &= ~htonl(0xff << 20);
279 ip6->ip6_flow |= htonl((u_int32_t)itos << 20);
280 break;
282 #endif /* INET6 */
283 default:
284 ipstat.ips_nogif++;
285 m_freem(m);
286 return;
288 gif_input(m, af, gifp);
289 return;
293 * validate outer address.
295 static int
296 gif_validate4(const struct ip *ip, struct gif_softc *sc, struct ifnet *ifp)
298 struct sockaddr_in *src, *dst;
299 struct in_ifaddr_container *iac;
301 src = (struct sockaddr_in *)sc->gif_psrc;
302 dst = (struct sockaddr_in *)sc->gif_pdst;
304 /* check for address match */
305 if (src->sin_addr.s_addr != ip->ip_dst.s_addr ||
306 dst->sin_addr.s_addr != ip->ip_src.s_addr)
307 return 0;
309 /* martian filters on outer source - NOT done in ip_input! */
310 if (IN_MULTICAST(ntohl(ip->ip_src.s_addr)))
311 return 0;
312 switch ((ntohl(ip->ip_src.s_addr) & 0xff000000) >> 24) {
313 case 0: case 127: case 255:
314 return 0;
316 /* reject packets with broadcast on source */
317 TAILQ_FOREACH(iac, &in_ifaddrheads[mycpuid], ia_link) {
318 struct in_ifaddr *ia4 = iac->ia;
320 if (!(ia4->ia_ifa.ifa_ifp->if_flags & IFF_BROADCAST))
321 continue;
322 if (ip->ip_src.s_addr == ia4->ia_broadaddr.sin_addr.s_addr)
323 return 0;
326 /* ingress filters on outer source */
327 if (!(sc->gif_if.if_flags & IFF_LINK2) && ifp != NULL) {
328 struct sockaddr_in sin;
329 struct rtentry *rt;
331 bzero(&sin, sizeof sin);
332 sin.sin_family = AF_INET;
333 sin.sin_len = sizeof(struct sockaddr_in);
334 sin.sin_addr = ip->ip_src;
335 rt = rtpurelookup((struct sockaddr *)&sin);
336 if (rt != NULL)
337 --rt->rt_refcnt;
338 if (rt == NULL || rt->rt_ifp != ifp) {
339 #if 0
340 log(LOG_WARNING, "%s: packet from 0x%x dropped "
341 "due to ingress filter\n", if_name(&sc->gif_if),
342 (u_int32_t)ntohl(sin.sin_addr.s_addr));
343 #endif
344 return 0;
348 return 32 * 2;
352 * we know that we are in IFF_UP, outer address available, and outer family
353 * matched the physical addr family. see gif_encapcheck().
356 gif_encapcheck4(const struct mbuf *m, int off, int proto, void *arg)
358 struct ip ip;
359 struct gif_softc *sc;
360 struct ifnet *ifp;
362 /* sanity check done in caller */
363 sc = (struct gif_softc *)arg;
365 /* LINTED const cast */
366 m_copydata(__DECONST(struct mbuf *, m), 0, sizeof ip, (caddr_t)&ip);
367 ifp = ((m->m_flags & M_PKTHDR) != 0) ? m->m_pkthdr.rcvif : NULL;
369 return gif_validate4(&ip, sc, ifp);
373 in_gif_attach(struct gif_softc *sc)
375 sc->encap_cookie4 = encap_attach_func(AF_INET, -1, gif_encapcheck,
376 &in_gif_protosw, sc);
377 if (sc->encap_cookie4 == NULL)
378 return EEXIST;
379 return 0;
383 in_gif_detach(struct gif_softc *sc)
385 int error;
387 error = encap_detach(sc->encap_cookie4);
388 if (error == 0)
389 sc->encap_cookie4 = NULL;
390 return error;
393 #endif /* INET */
|
{
"url": "https://repo.or.cz/dragonfly.git/blob/ea434b6fa505f0bbc28650a41494dea1ee26dd28:/sys/netinet/in_gif.c",
"source_domain": "repo.or.cz",
"snapshot_id": "crawl=CC-MAIN-2019-13",
"warc_metadata": {
"Content-Length": "111100",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:XVDGJX3A433LKSSQ5KEM4AG3ZMLPZ5BJ",
"WARC-Concurrent-To": "<urn:uuid:ca2bcc1f-11ae-486c-9ff2-d5c809007275>",
"WARC-Date": "2019-03-26T06:30:14Z",
"WARC-IP-Address": "195.113.20.142",
"WARC-Identified-Payload-Type": "application/xhtml+xml",
"WARC-Payload-Digest": "sha1:EOWULZLPQCSK3FP42GIJ254DFD7YZOPJ",
"WARC-Record-ID": "<urn:uuid:377451bd-6dbd-49de-ae0c-a3e9fc347bd2>",
"WARC-Target-URI": "https://repo.or.cz/dragonfly.git/blob/ea434b6fa505f0bbc28650a41494dea1ee26dd28:/sys/netinet/in_gif.c",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:85103c35-73e9-454e-92b7-081ffd8ce55f>"
},
"warc_info": "isPartOf: CC-MAIN-2019-13\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for March 2019\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-140-190-246.ec2.internal\r\nsoftware: Apache Nutch 1.15 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 0.11-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
27,
70,
115,
120,
200,
280,
340,
345,
350,
409,
434,
506,
578,
592,
663,
730,
804,
877,
951,
1025,
1100,
1148,
1225,
1300,
1380,
1457,
1537,
1614,
1689,
1769,
1848,
1924,
1942,
1967,
1993,
2019,
2045,
2072,
2099,
2124,
2150,
2177,
2204,
2232,
2259,
2290,
2313,
2339,
2366,
2399,
2426,
2457,
2488,
2519,
2552,
2583,
2599,
2627,
2637,
2668,
2698,
2739,
2754,
2822,
2842,
2878,
2919,
2988,
3035,
3051,
3066,
3082,
3111,
3174,
3198,
3205,
3269,
3319,
3390,
3459,
3528,
3591,
3612,
3629,
3675,
3713,
3751,
3767,
3792,
3814,
3830,
3848,
3867,
3893,
3926,
3959,
3971,
3991,
4022,
4044,
4055,
4066,
4083,
4102,
4127,
4153,
4187,
4221,
4233,
4253,
4290,
4337,
4348,
4359,
4372,
4389,
4455,
4468,
4479,
4495,
4520,
4553,
4591,
4638,
4686,
4724,
4735,
4751,
4775,
4799,
4844,
4875,
4931,
4966,
5020,
5029,
5082,
5114,
5164,
5207,
5247,
5268,
5324,
5344,
5404,
5454,
5510,
5546,
5589,
5636,
5675,
5711,
5741,
5770,
5780,
5813,
5824,
5860,
5886,
5922,
5938,
5962,
6020,
6063,
6079,
6113,
6123,
6176,
6199,
6210,
6270,
6289,
6298,
6336,
6367,
6386,
6398,
6417,
6437,
6455,
6478,
6507,
6538,
6556,
6587,
6631,
6689,
6705,
6729,
6741,
6764,
6783,
6804,
6820,
6843,
6862,
6880,
6913,
6946,
6958,
6970,
7001,
7037,
7089,
7098,
7149,
7160,
7171,
7188,
7211,
7236,
7255,
7274,
7308,
7342,
7354,
7366,
7403,
7451,
7487,
7533,
7542,
7587,
7628,
7679,
7690,
7713,
7726,
7750,
7766,
7778,
7806,
7818,
7848,
7863,
7943,
7978,
8015,
8061,
8107,
8141,
8194,
8241,
8255,
8321,
8369,
8383,
8444,
8476,
8490,
8540,
8600,
8637,
8695,
8709,
8773,
8787,
8829,
8890,
8918,
8942,
8971,
9001,
9047,
9078,
9126,
9146,
9167,
9210,
9220,
9273,
9326,
9370,
9381,
9395,
9414,
9493,
9555,
9628,
9646,
9672,
9695,
9733,
9767,
9795,
9868,
9937,
9977,
10017,
10088,
10114,
10149,
10168,
10182,
10222,
10237,
10282,
10302,
10332,
10350
],
"line_end_idx": [
27,
70,
115,
120,
200,
280,
340,
345,
350,
409,
434,
506,
578,
592,
663,
730,
804,
877,
951,
1025,
1100,
1148,
1225,
1300,
1380,
1457,
1537,
1614,
1689,
1769,
1848,
1924,
1942,
1967,
1993,
2019,
2045,
2072,
2099,
2124,
2150,
2177,
2204,
2232,
2259,
2290,
2313,
2339,
2366,
2399,
2426,
2457,
2488,
2519,
2552,
2583,
2599,
2627,
2637,
2668,
2698,
2739,
2754,
2822,
2842,
2878,
2919,
2988,
3035,
3051,
3066,
3082,
3111,
3174,
3198,
3205,
3269,
3319,
3390,
3459,
3528,
3591,
3612,
3629,
3675,
3713,
3751,
3767,
3792,
3814,
3830,
3848,
3867,
3893,
3926,
3959,
3971,
3991,
4022,
4044,
4055,
4066,
4083,
4102,
4127,
4153,
4187,
4221,
4233,
4253,
4290,
4337,
4348,
4359,
4372,
4389,
4455,
4468,
4479,
4495,
4520,
4553,
4591,
4638,
4686,
4724,
4735,
4751,
4775,
4799,
4844,
4875,
4931,
4966,
5020,
5029,
5082,
5114,
5164,
5207,
5247,
5268,
5324,
5344,
5404,
5454,
5510,
5546,
5589,
5636,
5675,
5711,
5741,
5770,
5780,
5813,
5824,
5860,
5886,
5922,
5938,
5962,
6020,
6063,
6079,
6113,
6123,
6176,
6199,
6210,
6270,
6289,
6298,
6336,
6367,
6386,
6398,
6417,
6437,
6455,
6478,
6507,
6538,
6556,
6587,
6631,
6689,
6705,
6729,
6741,
6764,
6783,
6804,
6820,
6843,
6862,
6880,
6913,
6946,
6958,
6970,
7001,
7037,
7089,
7098,
7149,
7160,
7171,
7188,
7211,
7236,
7255,
7274,
7308,
7342,
7354,
7366,
7403,
7451,
7487,
7533,
7542,
7587,
7628,
7679,
7690,
7713,
7726,
7750,
7766,
7778,
7806,
7818,
7848,
7863,
7943,
7978,
8015,
8061,
8107,
8141,
8194,
8241,
8255,
8321,
8369,
8383,
8444,
8476,
8490,
8540,
8600,
8637,
8695,
8709,
8773,
8787,
8829,
8890,
8918,
8942,
8971,
9001,
9047,
9078,
9126,
9146,
9167,
9210,
9220,
9273,
9326,
9370,
9381,
9395,
9414,
9493,
9555,
9628,
9646,
9672,
9695,
9733,
9767,
9795,
9868,
9937,
9977,
10017,
10088,
10114,
10149,
10168,
10182,
10222,
10237,
10282,
10302,
10332,
10350,
10371
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 10371,
"ccnet_original_nlines": 300,
"rps_doc_curly_bracket": 0.0019284499576315284,
"rps_doc_ldnoobw_words": 1,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.0804813802242279,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.07709664851427078,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.534035325050354,
"rps_doc_frac_unique_words": 0.5511751174926758,
"rps_doc_mean_word_length": 5.451099395751953,
"rps_doc_num_sentences": 112,
"rps_doc_symbol_to_word_ratio": 0.01805189996957779,
"rps_doc_unigram_entropy": 6.036001682281494,
"rps_doc_word_count": 1319,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.020862309262156487,
"rps_doc_frac_chars_dupe_6grams": 0.014186370186507702,
"rps_doc_frac_chars_dupe_7grams": 0.014186370186507702,
"rps_doc_frac_chars_dupe_8grams": 0.014186370186507702,
"rps_doc_frac_chars_dupe_9grams": 0.014186370186507702,
"rps_doc_frac_chars_top_2gram": 0.01223921962082386,
"rps_doc_frac_chars_top_3gram": 0.0069540999829769135,
"rps_doc_frac_chars_top_4gram": 0.006258689798414707,
"rps_doc_books_importance": -1088.103759765625,
"rps_doc_books_importance_length_correction": -1088.103759765625,
"rps_doc_openwebtext_importance": -517.4227294921875,
"rps_doc_openwebtext_importance_length_correction": -517.4227294921875,
"rps_doc_wikipedia_importance": -408.18048095703125,
"rps_doc_wikipedia_importance_length_correction": -408.18048095703125
},
"fasttext": {
"dclm": 0.4774448275566101,
"english": 0.2824690639972687,
"fineweb_edu_approx": 2.064797878265381,
"eai_general_math": 0.5790014863014221,
"eai_open_web_math": 0.05261706933379173,
"eai_web_code": 0.26661646366119385
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.678",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "4",
"label": "Analyze"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "4",
"label": "Code/Software"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "3",
"label": "Academic Writing"
}
},
"reasoning_depth": {
"primary": {
"code": "4",
"label": "Advanced Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "4",
"label": "Graduate/Expert Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
522,420,968,291,317,570
|
Using Mongrel but not Rails?
Hi,
This is not really rails related... but a question about Mongrel. I
can't seem to find this information anywhere. We've got an application
here running Apache Solr/Lucene and am interested in having a cluster
of Mogrel's + Apache w/load balancer run it. Anyone have any idea how
this can be done? Any of the most tiniest of hints would be greatly
cherished!
Matt
I don't know offhand, but there is a mongrel user's list:
http://rubyforge.org/mailman/listinfo/mongrel-users
Matt,
I recently had to write a service that ran on "raw Mongrel". An
online copy of the docs are available here:
<http://mongrel.rubyforge.org/rdoc/>
Most of my heavy lifting was done inside a Mongrel::HttpHandler
registered with the server. I'd start with the Mongrel::HttpServer
documentation, and there are examples scattered throughout.
-Mike
|
{
"url": "https://discuss.rubyonrails.org/t/using-mongrel-but-not-rails/11154",
"source_domain": "discuss.rubyonrails.org",
"snapshot_id": "crawl=CC-MAIN-2020-40",
"warc_metadata": {
"Content-Length": "16462",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:UTBVXT6ET2QKYVZXOII43QLXPNK6X3IG",
"WARC-Concurrent-To": "<urn:uuid:55ac1918-045a-4746-b225-45c297164cf1>",
"WARC-Date": "2020-09-26T01:15:58Z",
"WARC-IP-Address": "64.71.168.201",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:ICNKFXNU74MZUR4LFCGBSRCVE7PDGJWP",
"WARC-Record-ID": "<urn:uuid:63d736a3-75de-4257-a5df-d22ad5f7e1f3>",
"WARC-Target-URI": "https://discuss.rubyonrails.org/t/using-mongrel-but-not-rails/11154",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:2411018a-ad5b-4d9a-ac5c-a958b8e6370e>"
},
"warc_info": "isPartOf: CC-MAIN-2020-40\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for September 2020\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-89.ec2.internal\r\nsoftware: Apache Nutch 1.17 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.2-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
29,
30,
34,
35,
103,
174,
244,
314,
382,
393,
394,
399,
400,
458,
510,
511,
517,
518,
582,
626,
663,
664,
728,
795,
855,
856
],
"line_end_idx": [
29,
30,
34,
35,
103,
174,
244,
314,
382,
393,
394,
399,
400,
458,
510,
511,
517,
518,
582,
626,
663,
664,
728,
795,
855,
856,
861
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 861,
"ccnet_original_nlines": 26,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3664921522140503,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.020942410454154015,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.2146596908569336,
"rps_doc_frac_unique_words": 0.7230769395828247,
"rps_doc_mean_word_length": 5.169230937957764,
"rps_doc_num_sentences": 14,
"rps_doc_symbol_to_word_ratio": 0.00523559981957078,
"rps_doc_unigram_entropy": 4.411742687225342,
"rps_doc_word_count": 130,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.014880949631333351,
"rps_doc_frac_chars_top_3gram": 0,
"rps_doc_frac_chars_top_4gram": 0,
"rps_doc_books_importance": -71.20187377929688,
"rps_doc_books_importance_length_correction": -71.20187377929688,
"rps_doc_openwebtext_importance": -63.2099609375,
"rps_doc_openwebtext_importance_length_correction": -58.76838684082031,
"rps_doc_wikipedia_importance": -39.17163848876953,
"rps_doc_wikipedia_importance_length_correction": -39.17163848876953
},
"fasttext": {
"dclm": 0.022664900869131088,
"english": 0.9321880340576172,
"fineweb_edu_approx": 1.2158597707748413,
"eai_general_math": 0.7331399321556091,
"eai_open_web_math": 0.17809075117111206,
"eai_web_code": 0.33147066831588745
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.4",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.678",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "1",
"label": "No Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "6",
"label": "Not Applicable/Indeterminate"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
7,354,067,854,705,487,000
|
Is it possible to find all S3 buckets given a prefix
0 votes
l have multiple buckets with an application prefix and a region suffix e.g. Bucket names
• myapp-us-east-1
• myapp-us-west-1
Is there a way of finding all buckets given a certain prefix? Is there something like:
s3 = boto3.resource('s3') buckets = s3.buckets.filter(Prefix="myapp-")
Aug 27, 2018 in AWS by datageek
• 2,530 points
6,003 views
1 answer to this question.
0 votes
The high level collection command s3.buckets.filter only work for ways that document under describe_tags Filters. In such case, you MUST tag your bucket (s3.BucketTagging) before you can use the very specific filtering method s3.buckets.filter(Filters=formatted_tag_filter)
Currently, you can do this
s3 = boto3.resource('s3')
for bucket in s3.buckets.all():
if bucket.name.startswith("myapp-")"
print bucket.name
And following is example code given to filter out KEYS
# S3 list all keys with the prefix '/photos'
s3 = boto3.resource('s3')
for bucket in s3.buckets.all():
if bucket.name.startswith("myapp-")" :
for obj in bucket.objects.filter(Prefix='/photos'):
print('{0}:{1}'.format(bucket.name, obj.key))
Try this out
answered Aug 27, 2018 by Archana
• 4,170 points
Related Questions In AWS
0 votes
1 answer
0 votes
1 answer
Is it possible to add a compatibility layer above AWS?
Well there are few tools like TyphoonAE ...READ MORE
answered Jan 15, 2019 in AWS by Archana
• 5,640 points
310 views
0 votes
1 answer
+2 votes
1 answer
If s3 is global then why we need to select a region while launching it?
This might help you with your query. Have ...READ MORE
answered Feb 18, 2020 in AWS by Sirajul
• 59,230 points
910 views
0 votes
1 answer
POST request to S3 is returning a HTTPResponse 405
This error has nothing to do with ...READ MORE
answered Aug 13, 2018 in AWS by Archana
• 4,170 points
4,329 views
0 votes
1 answer
How to upload a file to Amazon S3 without passing it my server?
This article pretty much explains the entire ...READ MORE
answered Aug 14, 2018 in AWS by Archana
• 4,170 points
2,828 views
webinar REGISTER FOR FREE WEBINAR X
REGISTER NOW
webinar_success Thank you for registering Join Edureka Meetup community for 100+ Free Webinars each month JOIN MEETUP GROUP
|
{
"url": "https://www.edureka.co/community/17020/is-it-possible-to-find-all-s3-buckets-given-a-prefix?show=17022",
"source_domain": "www.edureka.co",
"snapshot_id": "CC-MAIN-2023-40",
"warc_metadata": {
"Content-Length": "175765",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:XHDPDYB4B4BCXGP2PGV4V5WSLVM2KCXB",
"WARC-Concurrent-To": "<urn:uuid:db47147c-7a28-46cd-941c-c5911809a571>",
"WARC-Date": "2023-09-23T16:50:03Z",
"WARC-IP-Address": "18.160.10.102",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:O3VERU6CIGHT6XJFV57AGKZO5SI7EUJF",
"WARC-Record-ID": "<urn:uuid:416d4881-6638-42a7-8228-960d31aa5a2c>",
"WARC-Target-URI": "https://www.edureka.co/community/17020/is-it-possible-to-find-all-s3-buckets-given-a-prefix?show=17022",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:713295b3-d9a1-4ec6-865b-3a0c897ab642>"
},
"warc_info": "isPartOf: CC-MAIN-2023-40\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for September/October 2023\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-159\r\nsoftware: Apache Nutch 1.19 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.5-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
53,
54,
62,
63,
152,
153,
173,
174,
194,
195,
282,
283,
354,
355,
387,
402,
414,
415,
442,
443,
451,
452,
726,
727,
754,
755,
781,
814,
854,
877,
933,
978,
1004,
1036,
1079,
1139,
1197,
1210,
1243,
1258,
1259,
1284,
1285,
1293,
1302,
1310,
1319,
1320,
1375,
1376,
1429,
1430,
1470,
1485,
1495,
1503,
1512,
1521,
1530,
1531,
1603,
1604,
1660,
1661,
1701,
1717,
1727,
1735,
1744,
1745,
1796,
1797,
1844,
1845,
1885,
1900,
1912,
1920,
1929,
1930,
1994,
1995,
2053,
2054,
2094,
2109,
2121,
2157,
2170
],
"line_end_idx": [
53,
54,
62,
63,
152,
153,
173,
174,
194,
195,
282,
283,
354,
355,
387,
402,
414,
415,
442,
443,
451,
452,
726,
727,
754,
755,
781,
814,
854,
877,
933,
978,
1004,
1036,
1079,
1139,
1197,
1210,
1243,
1258,
1259,
1284,
1285,
1293,
1302,
1310,
1319,
1320,
1375,
1376,
1429,
1430,
1470,
1485,
1495,
1503,
1512,
1521,
1530,
1531,
1603,
1604,
1660,
1661,
1701,
1717,
1727,
1735,
1744,
1745,
1796,
1797,
1844,
1845,
1885,
1900,
1912,
1920,
1929,
1930,
1994,
1995,
2053,
2054,
2094,
2109,
2121,
2157,
2170,
2293
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 2293,
"ccnet_original_nlines": 89,
"rps_doc_curly_bracket": 0.001744439941830933,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.24654832482337952,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.06311637163162231,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.3155818581581116,
"rps_doc_frac_unique_words": 0.5169491767883301,
"rps_doc_mean_word_length": 4.8728814125061035,
"rps_doc_num_sentences": 38,
"rps_doc_symbol_to_word_ratio": 0.009861930273473263,
"rps_doc_unigram_entropy": 4.871585845947266,
"rps_doc_word_count": 354,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.16289855539798737,
"rps_doc_frac_chars_dupe_6grams": 0.11130435019731522,
"rps_doc_frac_chars_dupe_7grams": 0.11130435019731522,
"rps_doc_frac_chars_dupe_8grams": 0.11130435019731522,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.024347830563783646,
"rps_doc_frac_chars_top_3gram": 0.04173912853002548,
"rps_doc_frac_chars_top_4gram": 0.037681158632040024,
"rps_doc_books_importance": -229.82968139648438,
"rps_doc_books_importance_length_correction": -229.82968139648438,
"rps_doc_openwebtext_importance": -141.4490203857422,
"rps_doc_openwebtext_importance_length_correction": -141.4490203857422,
"rps_doc_wikipedia_importance": -160.5797882080078,
"rps_doc_wikipedia_importance_length_correction": -160.5797882080078
},
"fasttext": {
"dclm": 0.1775885820388794,
"english": 0.8298158645629883,
"fineweb_edu_approx": 1.478698492050171,
"eai_general_math": 0.10373842716217041,
"eai_open_web_math": 0.2358628511428833,
"eai_web_code": 0.0007182999979704618
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.678",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-1,388,460,087,490,515,700
|
Introduce a mechanism to trace boot sequence.
This CL adds a trigger and a service so that Systrace can be used
for tracing events during boot.
persist.debug.atrace.boottrace property is used for switching on
and off tracing during boot. /data/misc/boottrace/categories
file is used for specifying the categories to be traced.
These property and file are rewritten by Systrace when the newly
added option --boot is specified.
Here is an example of tracing events of am and wm catetories
during boot.
$ external/chromium-trace/systrace am wm --boot
This command will cause the device to reboot. Once the device has
booted up, the trace report is created by hitting Ctrl+C.
As written in readme.txt, this mechanism relies on persistent
property, so tracing events that are emitted before that are not
recorded. This is enough for tracing events after zygote is
launched though.
This only works on userdebug or eng build for security reason.
BUG: 21739901
Change-Id: I03f2963d77a678f47eab5e3e29fc7e91bc9ca3a4
3 files changed
|
{
"url": "https://android.googlesource.com/platform/system/core/+/f93db4b",
"source_domain": "android.googlesource.com",
"snapshot_id": "crawl=CC-MAIN-2018-17",
"warc_metadata": {
"Content-Length": "13042",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:UDG2ZRURDI3OJDLMLRIFZJK6HP4I6JVI",
"WARC-Concurrent-To": "<urn:uuid:592bae93-e42f-4714-93e0-35785455a89e>",
"WARC-Date": "2018-04-22T22:19:42Z",
"WARC-IP-Address": "209.85.201.82",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:ON6T7F4BONL26ICRBCDK27RIA2XLQDX5",
"WARC-Record-ID": "<urn:uuid:cd962979-e14b-4af6-9a92-f8ce17d9ebd7>",
"WARC-Target-URI": "https://android.googlesource.com/platform/system/core/+/f93db4b",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:c648039a-61e8-4489-97eb-d2a3cf09b1fd>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-168-23-116.ec2.internal\r\nsoftware: Nutch 1.6 (CC)\r\nisPartOf: CC-MAIN-2018-17\r\noperator: Common Crawl Admin\r\ndescription: Wide crawl of the web for April 2018\r\npublisher: Common Crawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
46,
47,
113,
145,
210,
271,
328,
393,
427,
428,
489,
502,
503,
551,
552,
618,
676,
677,
739,
804,
864,
881,
944,
945,
959,
1012
],
"line_end_idx": [
46,
47,
113,
145,
210,
271,
328,
393,
427,
428,
489,
502,
503,
551,
552,
618,
676,
677,
739,
804,
864,
881,
944,
945,
959,
1012,
1027
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 1027,
"ccnet_original_nlines": 26,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.36180904507637024,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.015075379982590675,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.17085427045822144,
"rps_doc_frac_unique_words": 0.6129032373428345,
"rps_doc_mean_word_length": 5.36774206161499,
"rps_doc_num_sentences": 16,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.33847713470459,
"rps_doc_word_count": 155,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.0625,
"rps_doc_frac_chars_top_3gram": 0.03846153989434242,
"rps_doc_frac_chars_top_4gram": 0,
"rps_doc_books_importance": -82.63483428955078,
"rps_doc_books_importance_length_correction": -82.63483428955078,
"rps_doc_openwebtext_importance": -47.232582092285156,
"rps_doc_openwebtext_importance_length_correction": -33.65301513671875,
"rps_doc_wikipedia_importance": -33.39994430541992,
"rps_doc_wikipedia_importance_length_correction": -33.39994430541992
},
"fasttext": {
"dclm": 0.34620821475982666,
"english": 0.9009157419204712,
"fineweb_edu_approx": 2.471097707748413,
"eai_general_math": 0.35888880491256714,
"eai_open_web_math": 0.1990770697593689,
"eai_web_code": 0.42457348108291626
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.4",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.02",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "4",
"label": "Code/Software"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "23",
"label": "Tutorial"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "4",
"label": "Graduate/Expert Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-7,415,834,229,013,576,000
|
Better JavaScript Minification
Issue № 304
Better JavaScript Minification
In the past few years, performance research has become more prevalent thanks to research by the Yahoo! Exceptional Performance Team and Google’s Steve Souders. Most of that research studies not the individual HTML page, but the resources the page requires to display or behave correctly.
Article Continues Below
Although both CSS and JavaScript may be included within an HTML page, best practices encourage storing CSS and JavaScript in external files that can be downloaded and cached separately. Performance research asks: How can these external resources be downloaded and applied most efficiently? The first approach is to limit the number of external requests since the overhead of each HTTP request is high. The second approach? Make your code as small as possible.
The history of JavaScript byte savings#section2
Douglas Crockford introduced JSMin in 2004 as a way to shrink JavaScript files before placing them into a production environment. His simple tool removed spaces, tabs, and comments from JavaScript files, effectively decreasing the size compared to the original source file. His rationale was sound: decreasing the size of JavaScript code results in faster downloads and a better user experience.
Three years later, Yahoo! engineer Julien Lecomte introduced the YUI Compressor. The YUI Compressor’s goal was to shrink JavaScript files even further than JSMin by applying smart optimizations to the source code. In addition to removing comments, spaces, and tabs, the YUI Compressor also safely removes line breaks, further decreasing the overall file size. The biggest byte savings, though, come from replacing local variable names with one- or two-character names. For example, suppose you have the following function:
function sum(num1, num2) {
return num1 + num2;
}
YUI Compressor changes this to:
function sum(A,B){return A+B;}
Note that the two local variables, num1 and num2, were replaced by A and B, respectively. Since YUI Compressor actually parses the entire JavaScript input, it can safely replace local variable names without introducing code errors. The overall function continues to work as it did originally since the variable names are irrelevant to the functionality. On average, the YUI Compressor can compress files up to 18% more than JSMin.
These days, it’s common to use a minification tool plus HTTP compression to further reduce JavaScript file size. This results in even greater savings than using either method alone.
Boosting minification#section3
A couple of years ago, as I started debugging large amounts of production code, I realized that the YUI Compressor didn’t apply variable replacement to a fairly significant portion of my code. Bothered by what I considered a lot of wasted bytes, I explored coding patterns to boost the YUI Compressor’s minification powers. I presented my results, Extreme JavaScript Compression with YUI Compressor, internally at Yahoo!.
In my investigation, I discovered coding patterns that prevented YUI Compressor from performing variable name replacement. By modifying or avoiding these coding patterns, you can improve the YUI Compressor’s performance.
JavaScript’s evil features#section4
Anyone who has followed Douglas Crockford’s writing or lectures knows about the “evil” parts of JavaScript: The parts that are confusing and/or that prevent us from writing clean code that performs well. The eval() function and the with statement are the two most egregious examples of evil JavaScript. Though there are other considerations, both of these features force YUI Compressor to stop replacing variables. To understand why, we need to understand the intricacies of how each works.
Working with eval()#section5
The eval() statement’s job is to take a string and interpret it as JavaScript code. For example:
eval("alert('Hello world!');");
The tricky part of eval() is that it has access to all of the variables and functions that exist around it. Here’s a more complex example:
var message = "Hello world!";function doSomething() {
eval("alert(message)");
}
When you call doSomething(), an alert is displayed with the message, “Hello world!”. That’s because the string passed into eval() accesses the global variable message and displays it. Now consider what would happen if you automatically replaced the variable name message:
var A = "Hello world!";function doSomething() {
eval("alert(message)");
}
Note that changing the variable name to A results in an error when doSomething() executes (since message is undefined). YUI Compressor’s first job is to preserve the functionality of your script, and so when it sees eval(), it stops replacing variables. This might not sound like such a bad idea until you realize the full implications: Variable name replacement is prevented not only in the local context where eval() is called, but in all containing contexts as well. In the previous example, this means that both the context inside of doSomething() and the global context cannot have variable names replaced.
Using eval() anywhere in your code means that global variable names will never be changed. Consider the following example:
function handleJSONP(object) {
return object;
}function interpretJSONP(code) {
var data = eval(code);
//process data
}
In this code, pretend that handleJSONP() and interpretJSONP() are defined in the midst of other functions. JSONP is a widely used Ajax communication format that requires the response to be interpreted by the JavaScript engine. For this example, a sample JSONP response might look like this:
handleJSONP({message:"Hello world!"});
If you received this code back from the server via an XMLHttpRequest call, the next step is to evaluate it, at which point eval() becomes very useful. But just having eval() in the code means that none of the global identifiers can have their names replaced. The best option is to limit the number of global variables you introduce.
You can often get away with this by creating a self-executing anonymous function, such as:
(function() {
function handleJSONP(object) {
return object;
} function interpretJSONP(code) {
var data = eval(code);
//process data
}
})();
This code introduces no new global variables, but since eval() is used, none of the variable names will be replaced. The actual result (110 bytes) is:
(Line wraps marked » —Ed.)
(function(){function handleJSONP(object){return object}function »
interpretJSONP(code){var data=eval(code)}})();
The nice thing about JSONP is that it relies on the existence of just one global identifier, the function to which the result must be passed (in this case, handleJSONP()). This means that it doesn’t need access to any local variables or functions and gives you the opportunity to sequester the eval() function in its own global function. Note that you also must move handleJSONP() outside to be global as well so its name doesn’t get replaced:
//my own eval
function myEval(code) {
return eval(code);
}function handleJSONP(object) {
return object;
}(function() {
function interpretJSONP(code) {
var data = myEval(code);
//process data
}
})();
The function myEval() now acts like eval() except that it cannot access local variables. It can, however, access all global variables and functions. If the code being executed by eval() will never need access to local variables, then this approach is the best. By keeping the only reference to eval() outside of the anonymous function, you allow every variable name inside of that function to be replaced. Here’s the output:
function myEval(code){return eval(code)}function handleJSONP »
(a){return a}(function(){function a(b){var c=myEval(b)}})();
You can see that both interpretJSON(), code, and data were replaced (with a, b, and c, respectively). The result is 120 bytes, which you’ll note is larger than the example without eval() sequestered. That doesn’t mean the approach is faulty, it’s just that this example code is far too small to see an impact. If you were to apply this change on 100KB of JavaScript code, you would see that the resulting code is much smaller than leaving eval() in place.
Of course, the best option is not to use eval() at all, as you’ll avoid a lot of hoop-jumping to make the YUI Compressor happy. However, if you must, then sequestering the eval() function is your best bet for optimal minification.
The with statement#section6
The with statement is the second evil feature that interferes with the YUI Compressor’s variable replacement technique. For those unfamiliar, the with statement is designed (in theory) to reduce the size of code by eliminating the need to write the same variable names over and over again. Consider the following:
var object = {
message: "Hello, ",
messageSuffix: ", and welcome."
};
object.message += "world" + object.messageSuffix;
alert(object.message);
The with statement allows you to rewrite this code as:
var object = {
message: "Hello, ",
messageSuffix: ", and welcome."
};
with (object) {
message += "world" + messageSuffix;
alert(message);
}
Effectively, the with statement avoids the need to repeat “object” multiple times within the code. But these savings come at a cost. First, there are performance implications from using the with statement, as local variables become slower to access. This happens because variables inside of a with statement are ambiguous until execution time: They may be properties of the with statement’s context object or they may be variables from the function or another execution context. To understand this ambiguity better, take a look at the code when the local variable message is added and the definition of object is removed:
var message = "Yo, ";with (object) {
message += "world" + messageSuffix;
alert(message);
}
When the identifier message is used inside of the with statement, it could be referencing the local variable message or it could be referencing a property named message on object. Since JavaScript is a late binding language, there is no way to know the true reference for message without completely executing the code and determining if object has a property named message. Witness how late binding affects this code:
function displayMessage(object) {
var message = "Yo, "; with (object){
message += "world" + messageSuffix;
alert(message);
}
}displayMessage({ message: "Hello, ", messageSuffix: ", and welcome." });
displayMessage({ messageSuffix: ", and welcome." });
The first time that displayMessage() is called, the object passed in has a property named message. When the with statement executes, the reference to message is mapped to the object property and so the displayed message is, “Hello, world, and welcome.” The second time, the object passed in has only the messageSuffix property, meaning the reference to message inside of the with statement refers to the local variable and the message displayed is therefore, “Yo, world, and welcome.”
Since the YUI Compressor doesn’t actually execute the JavaScript code, it has no way of knowing whether identifiers in a with statement are object properties (in which case, it is not safe to replace them) or local variable references (in which case, it is safe to replace them). The YUI Compressor treats the with statement the same as eval(): when present, it will not perform variable replacement on the function or any containing execution contexts.
Unlike eval(), there is no way to sequester the with statement in such a way that it doesn’t affect most of the code. The recommendation is to avoid using the with statement at all. Even though it appears to save bytes at the time of code writing, you actually end up losing bytes by forfeiting YUI Compressor’s variable replacement feature. The displayMessage() function gets minified like this:
function displayMessage(object){var message="Yo, ";with(object) »
{message+="world"+messageSuffix;alert(message)}};
This result is 112 bytes. If the function is rewritten to avoid the with statement, displayMessage() looks like this:
function displayMessage(object) {
var message = "Yo, "; object.message += "world" + object.messageSuffix;
alert(object.message);
}
When minified, this new version of the function becomes:
function displayMessage(a){var b="Yo, ";a.message+="world"+ »
a.messageSuffix;alert(a.message)};
The size of this result is 93 bytes, so even though the original source code is larger. The minified source code becomes smaller because we used variable replacement.
Conclusion#section7
YUI Compressor’s variable replacement functionality can give big byte savings while minifying your JavaScript. Since the YUI Compressor tries to avoid breaking your code by incorrectly replacing variable names, it will turn off variable replacement when the eval() function or with statement is used. These “evil” features alter how JavaScript code is interpreted and prevent the YUI Compressor from safely replacing variable names, which costs you a large amount of byte savings. Avoid this penalty by steering clear of eval() or sequester it away from the rest of your code. Also, avoid the with statement. These steps will ensure that your code doesn’t get in the way of optimal minification.
21 Reader Comments
1. That is partially true. The Closure Compiler can result in smaller code by manipulating the underlying code structure, but it doesn’t do safe variable name replacement. In the presence of eval(), you could end up with broken code as it doesn’t turn variable replacement off. It also performs other optimizations that may result in unintended changes to your code’s functionality. While it shows promise, I’m not ready to recommend the Closure Compiler over the YUI Compressor.
2. 1. eval and with are JavaScript features you should *generally* avoid. This is regardless of whether you are using any minification tool. Minification is quite possibly the *least* of the reasons why eval and with are evil.
2. The following practices are similar to eval, and should be avoided for the same reasons:
– using the Function constructor
– passing strings to window.setTimeout or window.setInterval
“why with is evil”:http://www.yuiblog.com/blog/2006/04/11/with-statement-considered-harmful/ and “why eval is evil”:http://xkr.us/js/eval
3. Really nice article Nicholas. I can’t really get into the details of the usage of eval and with but i can easily say that, not only in Javascript but with any language you write your code in, optimizing the code is something any developer should do 🙂
4. I can see some issues as well with the usage of eval and with, but i still concur that you have to minify your javascript somehow. It’s just a matter of choice imho.
Nice article.
5. Thanks for the comments, everyone. Just to clarify: the point of the article was not to simply say “avoid doing this,” but rather to give a clear description of *why* to avoid doing this (as I think everyone has heard “don’t use eval” and “don’t use with”, but rarely is there a nice description of why).
6. Fantastic article and a great eye-opener. However, when most of the internet-using world could be on lightning fast connections within half a decade, is it still going to be such a huge deal to save a couple of kb here and there?
7. Having smaller files and your website downoading faster can have SEO benefits, and this is meant to be more apparent since the Google Caffeine update, so keeping your code as lightweight as possible could be very useful in terms of ranking plus it could help with improving user experience.
However I think it is always good to try and do things in the best possible manner.
8. Keep in mind that lightning-fast connections are still bound by physical distance. The further the bytes have to travel, the longer it will take to get there, so if I request a byte from China it takes longer to receive than if I request that same byte from next door. Also, developing countries don’t have as much high speed internet penetration as the United States. There is still a significant portion of the world that accesses the internet over modem (or equivalent).
9. No serious coder (most of the people that would be reading this article) has used either eval or with since the stone age. Reasons:
# They introduce security vulnerabilities
# They are slow _aside from compression_
# They are difficult to debug
One more reason is hardly worth an alistapart article, IMO.
That being said, it was very well written.
10. @Joss internet connections may be getting faster but there’s two very good reasons why you should be concerned with these sort of code optimisations:
# Access to the Internet via mobiles is increasing at a much faster rate than for desktops, and file size is still a concern for most, not only in how long you have to wait, but in how much you have to pay.
# Google has just announced that page speed will be included in their algorithm for search results, so page optimisation will also be an SEO factor.
11. @Aaron – You would be surprised. There are definitely people still using “with”, but moreso eval(). Since JSON became popular, and native JSON parsing has only recently been introduced, most JavaScript libraries used eval(), and as such, didn’t get the best compression of their code.
12. @Tasarım –
bq. optimizing the code is something any developer should do
I can’t agree with this — any developer should _be able_ to optimise code, but only when it is shown to be necessary. I completely agree with aaron and dsevil re the reasons not to use eval and with, but any kind of optimisation that reduces code readability/maintainability (and most do) should only be used when it has been proved that it is _essential_.
13. The compressed code is not debuggable anymore, since all of it is in 1 line (JavaScript Error messages tell only the line number on which the error occurred).
Google’s Closure Compiler has another problem in its maximum compression mode: it cannot recognize instances or properties which are dynamically addressed. Since Closure compiler does not detect its use, it will treat the instance/property as unused and remove its definition from the code.
More than that, the code is not readable anymore without the use of some source beautifier or unpacker.
In some cases, the minification leads to bigger compressed files – especially if one replaces window or document with a shorthand, because those cannot be compressed much further.
BTW, it helps to keep the memory footprint of your JS small even without compression. Since there is a lack for very small Toolkits, it started one myself: http://tinyjs.sf.net – in the next version, I want to remove those selectors which are not very useful in normal cases to an external plugin.
14. very nice and interesting article Nicholas – and thanks for telling us why not to use eval and with!
15. This is just my two cents, but really, I’m surprised by how much this “minification/optimization makes debugging harder” argument still comes up. A simple one step build process which takes your CSS and JS and minifies/optimizes it isn’t that hard to come up with. I use a little Ruby script for that but you can even do it by hand! Just make sure you are using an scm tool like Git (in case you screw something up) and also that you have separate development and staging directories.
16. As someone who is going to school for Graphic Design/Website Design. This is one of those articles that teaches you something that they don’t teach in school. This is something i’ll certainly keep in mind, when using JS. 🙂
17. I recommend this site for anyone who likes playing in the bingo hall but likes online aswell!bingo is very crazy and popular game.It is a game of chance in which each player has one or more cards printed with differently numbered squares on which to place markers when the respective numbers are drawn and announced by a caller.I like to play bingo online….http://www.888enjoy.eu..
Got something to say?
We have turned off comments, but you can see what folks had to say before we did so.
More from ALA
A Content Model Is Not a Design System
Why do so many content models still look more like design systems rather than reflecting structured data? Mike Wills takes us on a personal journey as he examines his own past experiences and invites us to conceive content models that articulate meaning and group related content together for use on any channel.
Content
Voice Content and Usability
In this excerpt from Voice Content and Usability, author Preston So talks about the messy, primordial nature of human speech and challenges with programming computers to deal with these complexities.
Content
|
{
"url": "https://alistapart.com/article/better-javascript-minification/",
"source_domain": "alistapart.com",
"snapshot_id": "crawl=CC-MAIN-2021-49",
"warc_metadata": {
"Content-Length": "97801",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:JEZ52BTVA3XKEC62YTYASDKUE652E7W2",
"WARC-Concurrent-To": "<urn:uuid:bb4f5518-7536-497f-947e-e1abb205397a>",
"WARC-Date": "2021-12-07T05:58:18Z",
"WARC-IP-Address": "199.16.173.72",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:KKLPMWJH3OF3ZTLELHWCQRPWNAOAYJ3M",
"WARC-Record-ID": "<urn:uuid:b9491d05-38c4-47a7-9ae5-44d35e69ed59>",
"WARC-Target-URI": "https://alistapart.com/article/better-javascript-minification/",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:5f3f1d5c-b22b-4c19-94cd-4a6fc08418f3>"
},
"warc_info": "isPartOf: CC-MAIN-2021-49\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for November/December 2021\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-133\r\nsoftware: Apache Nutch 1.18 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.3-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
31,
43,
44,
75,
76,
364,
365,
389,
390,
850,
851,
899,
900,
1296,
1297,
1820,
1821,
1848,
1872,
1874,
1875,
1907,
1908,
1939,
1940,
2371,
2372,
2554,
2555,
2586,
2587,
3009,
3010,
3231,
3232,
3268,
3269,
3760,
3761,
3790,
3791,
3888,
3889,
3921,
3922,
4061,
4062,
4116,
4144,
4146,
4147,
4419,
4420,
4468,
4497,
4499,
4500,
5112,
5113,
5236,
5237,
5268,
5287,
5320,
5347,
5352,
5371,
5373,
5374,
5665,
5666,
5705,
5706,
6039,
6040,
6131,
6132,
6146,
6181,
6204,
6245,
6276,
6281,
6304,
6310,
6316,
6317,
6468,
6469,
6496,
6497,
6563,
6610,
6611,
7055,
7056,
7070,
7094,
7117,
7149,
7168,
7183,
7219,
7252,
7257,
7280,
7286,
7292,
7293,
7718,
7719,
7782,
7843,
7844,
8300,
8301,
8532,
8533,
8561,
8562,
8876,
8877,
8892,
8916,
8952,
8955,
9005,
9028,
9029,
9084,
9085,
9100,
9124,
9160,
9163,
9179,
9219,
9239,
9241,
9242,
9864,
9865,
9902,
9942,
9962,
9964,
9965,
10383,
10384,
10418,
10462,
10506,
10530,
10536,
10610,
10663,
10664,
11149,
11150,
11604,
11605,
12002,
12003,
12069,
12119,
12120,
12238,
12239,
12273,
12352,
12379,
12381,
12382,
12439,
12440,
12502,
12537,
12538,
12705,
12706,
12726,
12727,
13423,
13424,
13443,
13444,
13926,
13927,
14156,
14157,
14253,
14290,
14355,
14356,
14498,
14499,
14755,
14756,
14927,
14928,
14946,
14947,
15257,
15258,
15493,
15494,
15790,
15791,
15879,
15880,
16359,
16360,
16497,
16498,
16544,
16589,
16623,
16624,
16688,
16689,
16736,
16737,
16893,
16894,
17105,
17258,
17259,
17550,
17551,
17569,
17570,
17635,
17636,
17997,
17998,
18163,
18164,
18459,
18460,
18568,
18569,
18753,
18754,
19056,
19057,
19164,
19165,
19656,
19657,
19886,
19887,
20275,
20276,
20298,
20299,
20384,
20385,
20399,
20400,
20439,
20440,
20753,
20761,
20762,
20790,
20791,
20991
],
"line_end_idx": [
31,
43,
44,
75,
76,
364,
365,
389,
390,
850,
851,
899,
900,
1296,
1297,
1820,
1821,
1848,
1872,
1874,
1875,
1907,
1908,
1939,
1940,
2371,
2372,
2554,
2555,
2586,
2587,
3009,
3010,
3231,
3232,
3268,
3269,
3760,
3761,
3790,
3791,
3888,
3889,
3921,
3922,
4061,
4062,
4116,
4144,
4146,
4147,
4419,
4420,
4468,
4497,
4499,
4500,
5112,
5113,
5236,
5237,
5268,
5287,
5320,
5347,
5352,
5371,
5373,
5374,
5665,
5666,
5705,
5706,
6039,
6040,
6131,
6132,
6146,
6181,
6204,
6245,
6276,
6281,
6304,
6310,
6316,
6317,
6468,
6469,
6496,
6497,
6563,
6610,
6611,
7055,
7056,
7070,
7094,
7117,
7149,
7168,
7183,
7219,
7252,
7257,
7280,
7286,
7292,
7293,
7718,
7719,
7782,
7843,
7844,
8300,
8301,
8532,
8533,
8561,
8562,
8876,
8877,
8892,
8916,
8952,
8955,
9005,
9028,
9029,
9084,
9085,
9100,
9124,
9160,
9163,
9179,
9219,
9239,
9241,
9242,
9864,
9865,
9902,
9942,
9962,
9964,
9965,
10383,
10384,
10418,
10462,
10506,
10530,
10536,
10610,
10663,
10664,
11149,
11150,
11604,
11605,
12002,
12003,
12069,
12119,
12120,
12238,
12239,
12273,
12352,
12379,
12381,
12382,
12439,
12440,
12502,
12537,
12538,
12705,
12706,
12726,
12727,
13423,
13424,
13443,
13444,
13926,
13927,
14156,
14157,
14253,
14290,
14355,
14356,
14498,
14499,
14755,
14756,
14927,
14928,
14946,
14947,
15257,
15258,
15493,
15494,
15790,
15791,
15879,
15880,
16359,
16360,
16497,
16498,
16544,
16589,
16623,
16624,
16688,
16689,
16736,
16737,
16893,
16894,
17105,
17258,
17259,
17550,
17551,
17569,
17570,
17635,
17636,
17997,
17998,
18163,
18164,
18459,
18460,
18568,
18569,
18753,
18754,
19056,
19057,
19164,
19165,
19656,
19657,
19886,
19887,
20275,
20276,
20298,
20299,
20384,
20385,
20399,
20400,
20439,
20440,
20753,
20761,
20762,
20790,
20791,
20991,
20998
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 20998,
"ccnet_original_nlines": 267,
"rps_doc_curly_bracket": 0.003143159905448556,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.39447540044784546,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.01793069951236248,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.19045311212539673,
"rps_doc_frac_unique_words": 0.2951582968235016,
"rps_doc_mean_word_length": 5.104282855987549,
"rps_doc_num_sentences": 188,
"rps_doc_symbol_to_word_ratio": 0.0029076801147311926,
"rps_doc_unigram_entropy": 5.881368637084961,
"rps_doc_word_count": 3222,
"rps_doc_frac_chars_dupe_10grams": 0.01082330010831356,
"rps_doc_frac_chars_dupe_5grams": 0.06044023111462593,
"rps_doc_frac_chars_dupe_6grams": 0.03982730954885483,
"rps_doc_frac_chars_dupe_7grams": 0.03222668170928955,
"rps_doc_frac_chars_dupe_8grams": 0.02687584049999714,
"rps_doc_frac_chars_dupe_9grams": 0.02383558079600334,
"rps_doc_frac_chars_top_2gram": 0.01343792024999857,
"rps_doc_frac_chars_top_3gram": 0.013620330020785332,
"rps_doc_frac_chars_top_4gram": 0.006749359890818596,
"rps_doc_books_importance": -1538.34228515625,
"rps_doc_books_importance_length_correction": -1538.34228515625,
"rps_doc_openwebtext_importance": -987.0283813476562,
"rps_doc_openwebtext_importance_length_correction": -987.0283813476562,
"rps_doc_wikipedia_importance": -892.3236694335938,
"rps_doc_wikipedia_importance_length_correction": -892.3236694335938
},
"fasttext": {
"dclm": 0.2065187692642212,
"english": 0.9016733765602112,
"fineweb_edu_approx": 2.453087568283081,
"eai_general_math": 0.8967532515525818,
"eai_open_web_math": 0.18619513511657715,
"eai_web_code": 0.8184226155281067
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.133",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.678",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "4",
"label": "Analyze"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "10",
"label": "Knowledge Article"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "4",
"label": "Advanced Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "4",
"label": "Graduate/Expert Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
7,344,429,361,983,714,000
|
Posts
Showing posts from January, 2014
PANDA, Reproducibility, and Open Science
tl;dr : PANDA now supports detached replays (you don't need the underlying VM image to run a replay), and they can be shared at a new site called PANDA Share . Hooray for reproducibility! One of the most inspiring developments of the past few years has been the push for open science , the movement to ensure that scientific publications, data, and software are freely available to all. In computer science, a big part of this has been a trend towards making software and experimental data available once a paper has been published, so that others can verify experiments and "stand on the shoulders of giants" by extending the software. There have also been initiatives aimed at making sure that the results of experiments in computer science can be replicated. In the latest release of PANDA, our Platform for Architecture-Neutral Dynamic Analysis, we've taken an important step in ensuring that experiments in dynamic analysis can be freely shared and replicated: as of c
|
{
"url": "https://moyix.blogspot.com/2014/01/",
"source_domain": "moyix.blogspot.com",
"snapshot_id": "CC-MAIN-2024-10",
"warc_metadata": {
"Content-Length": "82335",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:GN4KGZVMRM3MWKJ6F7BJRJJEVODPHVRY",
"WARC-Concurrent-To": "<urn:uuid:1215c851-06f2-45ac-8dcc-2143638dfa1c>",
"WARC-Date": "2024-03-04T02:16:36Z",
"WARC-IP-Address": "142.250.31.132",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:UBTH3IUJ36QZDHYOWYN5AJ43663F5FLB",
"WARC-Record-ID": "<urn:uuid:cb42acde-0c16-44e4-bc5a-243ee3580ad6>",
"WARC-Target-URI": "https://moyix.blogspot.com/2014/01/",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:89fe4df5-9525-4b15-b155-1da8bd69d503>"
},
"warc_info": "isPartOf: CC-MAIN-2024-10\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for February/March 2024\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-154\r\nsoftware: Apache Nutch 1.19 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.5-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
6,
7,
40,
41,
82,
83
],
"line_end_idx": [
6,
7,
40,
41,
82,
83,
1060
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 1060,
"ccnet_original_nlines": 6,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.42500001192092896,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.02500000037252903,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.12999999523162842,
"rps_doc_frac_unique_words": 0.6081871390342712,
"rps_doc_mean_word_length": 4.994152069091797,
"rps_doc_num_sentences": 6,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.406201362609863,
"rps_doc_word_count": 171,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.017564399167895317,
"rps_doc_frac_chars_top_3gram": 0.03981265053153038,
"rps_doc_frac_chars_top_4gram": 0,
"rps_doc_books_importance": -95.64324951171875,
"rps_doc_books_importance_length_correction": -95.64324951171875,
"rps_doc_openwebtext_importance": -50.768375396728516,
"rps_doc_openwebtext_importance_length_correction": -38.71630859375,
"rps_doc_wikipedia_importance": -35.016361236572266,
"rps_doc_wikipedia_importance_length_correction": -35.016361236572266
},
"fasttext": {
"dclm": 0.03772240877151489,
"english": 0.9354626536369324,
"fineweb_edu_approx": 2.2488250732421875,
"eai_general_math": 0.22423386573791504,
"eai_open_web_math": 0.2004358172416687,
"eai_web_code": 0.003058670088648796
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.019",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "025.04",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "Library science",
"level_3": "Library administration"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "9",
"label": "Personal/Misc"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "1",
"label": "Truncated Snippets"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "16",
"label": "Personal Blog"
},
"secondary": {
"code": "10",
"label": "Knowledge Article"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "6",
"label": "Not Applicable/Indeterminate"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
2,006,268,809,959,712,000
|
wingolog
visualizing statistical profiles with chartprof
9 February 2009 3:04 PM (scheme | guile | goops | profiling | valgrind | statprof | chartprof | cairo | visualization | compiler)
Greetings, hackers of the good hack!
In recent weeks, my good hack has been Guile's compiler and virtual machine. It's almost regression-free, and we're looking for a merge to master within a few weeks.
Things are looking really good. Compiled coded conses significantly less than the evaluator, loads quickly, runs quickly of course, and on top of that has all kinds of fun features. Recently we made metadata have no cost, as we write it after the program text of compiled procedures, which are normally just mmap'd from disk. (I stole this idea from a paper on Self.)
In addition to our tower of language compilers, I recently added a tower of decompilers: from value, to objcode, to bytecode, to assembly... with the possibility of adding future decompilers, potentially going all the way back to Scheme itself. We have all of the debugging information to do it nicely.
However, there are still some regressions. Probably the biggest one is that GOOPS, Guile's object system, actually loads up more slowly with the VM than with the evaluator. So I spend last week giving GOOPS a closer look.
the hunt begins
Turns out, the slowness is in the compiler. But why should the compiler be running at runtime, you ask? Well, it's the dynamic recompilation stuff I spoke of before.
GOOPS compiles implementations of methods for each set of types that it sees at runtime, which is pretty neat. The PIC paper by Hölzle, Chambers, and Ungar describe the advantages of this approach:
The presence of PIC-based [runtime] type information fundamentally alters the nature of optimization of dynamically-typed object-oriented languages. In “traditional” systems such as the current SELF compiler, type information is scarce, and consequently the compiler is designed to make the best possible use of the type information. This effort is expensive both in terms of compile time and compiled code space, since the heuristics in the compiler are tuned to spend time and space if it helps extract or preserve type information. In contrast, a PIC-based recompiling system has a veritable wealth of type information: every message has a set of likely receiver types associated with it derived from the previously compiled version’s PICs. The compiler’s heuristics and perhaps even its fundamental design should be reconsidered once the information in PICs becomes available...
(Thanks to Keith for pointing me to that paper.)
Anyway, recompilation was slow. So I then started to look at exactly why compilation was slow. I had callgrind, which is good, but doesn't give you enough information about *why* you are in those specific C procedures -- it's a C profile, not a Scheme profile. I had statprof, which is good, but doesn't give you enough information about the specific calltrees.
chartprof
So what to do? Well, since statistical profilers already have to walk the stacks, it was a simple matter to just to make statprof squirrel away the full stacks as they were sampled. Then, after the profiling run is done, you can process those stacks into call trees, and visualize that.
But how to visualize the call trees? I had some basic ideas of what I wanted, but no tool that I knew of that could present the information easily. But what I did have was an excellent toolbox: guile-cairo, and guile itself. So voilà chartprof:
Chartprof takes full call trees and produces a representation of where the time is spent. The cascading red part represents the control flow, as nested procedure invocations, and the numbers inside the red part indicate the cumulative time percentage spent in those procedure calls. The numbers out of the red part indicate "self time", when the sampler caught program execution in that procedure instead of in one of its call children.
If you click on the thumbnail on the left, you can download the whole thing. It's big: 1.2 megabytes. There's lots of information in there, is the thing. I should figure out how to prune that information, if that can be done so usefully.
I drew horizontal lines at any call that did not always dispatch to exactly one subcall. It's interesting, you do want to line up procedures and their call sites, but you don't want too many lines. This way seems to be a good compromise, though of course it's not the last word.
analysis
It seems that the culprit is a bit unfortunate. GOOPS, when it loads, enables extensibility in about 200 of Guile's primitive procedures, e.g. equal? and for-each, which allows those procedures to dispatch to methods of generic functions. Unfortunately, this slows down pattern matching in the compilers, as the pattern matcher uses equal?, and that ends up calling out to Scheme just to see if something is equal? to a symbol... badness, that.
The equal? is particularly egregious, as a call to scm_equal_p will do a number of built-in equality checks, then if they all fail it will dispatch to the equal? generic, which dispatches to a method that calls eqv?, which does some built-in checks, then dispatches to an eqv? generic, which finally returns #f just to say that 'foo is not the same as 'bar, something that should be a quick pointer comparison.
So I'm not exactly sure what I'm going to do to fix this, but at least now I know what to think about. I would have had no clue that it was the pattern matcher if it weren't for the the graphical visualization that chartprof gave me. So yay for turning optimization into a tools problem.
code
The code is in (charting prof) from git guile-charting, which in turn needs guile-lib from git.
I'd be interested in hearing feedback about the visualizations, particularly if people have other ideas about how to visualize call graphs. I also have some other information that I could present somehow: the arguments to the procedure applications, and the source locations of the call sites.
Happy hacking!
3 responses
1. Benjamin Otte says:
As for the right way to do charts, I prefer http://jrfonseca.blogspot.com/2007/12/profiling-dri-drivers.html
It looks way more intuitive than your solution.
2. wingo says:
Hey Benjamin. Those are indeed nice charts.
They're not sufficient for my purposes, though -- they're not dense enough, they do not distinguish multiple calls to the same procedure, and visually it is difficult to determine the proportionality of the various call trees.
My graphs might be a bit opaque, but at least they distinguish the various applications of map.
3. Brad Pitt Fight Club Jacket says:
This exertion is costly both regarding incorporate time and gathered code space, since the heuristics in the compiler are tuned to invest energy and space on the off chance that it concentrates or protect sort data.
Leave a Reply
|
{
"url": "http://wingolog.org/archives/2009/02/09/visualizing-statistical-profiles-with-chartprof",
"source_domain": "wingolog.org",
"snapshot_id": "crawl=CC-MAIN-2017-30",
"warc_metadata": {
"Content-Length": "13066",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:7YXERODCUENDE7YYFAQQ7HWL7EQ6BZO6",
"WARC-Concurrent-To": "<urn:uuid:c7752106-a44d-4e7c-ad00-e84e2f4ffd1a>",
"WARC-Date": "2017-07-21T04:28:46Z",
"WARC-IP-Address": "178.79.150.233",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:XRHRZFS5CZDSIEVCU537UZRJURWMWMOI",
"WARC-Record-ID": "<urn:uuid:4a6a7db0-f7a9-4f31-938b-ad578144fce3>",
"WARC-Target-URI": "http://wingolog.org/archives/2009/02/09/visualizing-statistical-profiles-with-chartprof",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:95fcbd6f-eb4e-487c-b7af-d7657c6be569>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-233-154-15.ec2.internal\r\nsoftware: Nutch 1.6 (CC)\r\nisPartOf: CC-MAIN-2017-30\r\noperator: Common Crawl Admin\r\ndescription: Wide crawl of the web for July 2017\r\npublisher: Common Crawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
9,
10,
58,
59,
189,
190,
227,
228,
394,
395,
763,
764,
1067,
1068,
1290,
1291,
1307,
1308,
1474,
1475,
1673,
1674,
2557,
2558,
2607,
2608,
2970,
2971,
2981,
2982,
3269,
3270,
3515,
3516,
3953,
3954,
4192,
4193,
4472,
4473,
4482,
4483,
4928,
4929,
5340,
5341,
5629,
5630,
5635,
5636,
5732,
5733,
6027,
6028,
6043,
6044,
6056,
6057,
6082,
6083,
6196,
6248,
6249,
6266,
6267,
6315,
6316,
6547,
6548,
6648,
6649,
6688,
6689,
6909,
6910
],
"line_end_idx": [
9,
10,
58,
59,
189,
190,
227,
228,
394,
395,
763,
764,
1067,
1068,
1290,
1291,
1307,
1308,
1474,
1475,
1673,
1674,
2557,
2558,
2607,
2608,
2970,
2971,
2981,
2982,
3269,
3270,
3515,
3516,
3953,
3954,
4192,
4193,
4472,
4473,
4482,
4483,
4928,
4929,
5340,
5341,
5629,
5630,
5635,
5636,
5732,
5733,
6027,
6028,
6043,
6044,
6056,
6057,
6082,
6083,
6196,
6248,
6249,
6266,
6267,
6315,
6316,
6547,
6548,
6648,
6649,
6688,
6689,
6909,
6910,
6923
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 6923,
"ccnet_original_nlines": 75,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.42867282032966614,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.023420870304107666,
"rps_doc_frac_lines_end_with_ellipsis": 0.013157890178263187,
"rps_doc_frac_no_alph_words": 0.16962385177612305,
"rps_doc_frac_unique_words": 0.4362356960773468,
"rps_doc_mean_word_length": 4.812664985656738,
"rps_doc_num_sentences": 78,
"rps_doc_symbol_to_word_ratio": 0.002838890068233013,
"rps_doc_unigram_entropy": 5.560540676116943,
"rps_doc_word_count": 1137,
"rps_doc_frac_chars_dupe_10grams": 0.03618421033024788,
"rps_doc_frac_chars_dupe_5grams": 0.03618421033024788,
"rps_doc_frac_chars_dupe_6grams": 0.03618421033024788,
"rps_doc_frac_chars_dupe_7grams": 0.03618421033024788,
"rps_doc_frac_chars_dupe_8grams": 0.03618421033024788,
"rps_doc_frac_chars_dupe_9grams": 0.03618421033024788,
"rps_doc_frac_chars_top_2gram": 0.005482459906488657,
"rps_doc_frac_chars_top_3gram": 0.007127190008759499,
"rps_doc_frac_chars_top_4gram": 0.006213449873030186,
"rps_doc_books_importance": -652.3507080078125,
"rps_doc_books_importance_length_correction": -652.3507080078125,
"rps_doc_openwebtext_importance": -428.67010498046875,
"rps_doc_openwebtext_importance_length_correction": -428.67010498046875,
"rps_doc_wikipedia_importance": -280.8353576660156,
"rps_doc_wikipedia_importance_length_correction": -280.8353576660156
},
"fasttext": {
"dclm": 0.09053797274827957,
"english": 0.9505143761634827,
"fineweb_edu_approx": 1.7216808795928955,
"eai_general_math": 0.8846240043640137,
"eai_open_web_math": 0.35168081521987915,
"eai_web_code": 0.6747058033943176
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.4",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "4",
"label": "Analyze"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "4",
"label": "Code/Software"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "16",
"label": "Personal Blog"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "4",
"label": "Graduate/Expert Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-4,215,957,668,400,571,000
|
Top Mud Sites Forum Return to TopMudSites.com
Go Back Top Mud Sites Forum > MUD Players and General Discussion > Tavern of the Blue Hand
Click here to Register
Reply
Thread Tools
Old 03-26-2012, 12:27 AM #1
meepo64
New Member
Join Date: Dec 2011
Posts: 4
meepo64 is on a distinguished road
Yet another looking for a mud request
I have been playing muds for a few months now and have jumped around to a variety of them.
What I have been looking for is a mud that does not rely on guilds, has plenty of quests, and has a robust crafting system. I am not opposed to guilds that are formed among players as a means of solidarity and offering help and perks. I just don't prefer the muds where they force/encourage membership in an established guild, which, in turn, dictates quite a bit about your character's development. I enjoy exploring the intricacies of the land around, crafting items, food, etc. to help in survival and a means of commerce, in a non-pvp environment.
I also enjoy quests, and a mud where talking to an npc to see if a quest/task is available does not become a frustrating long process of scouring help files, asking players who won't give you a solid answer for fear of spoilers, just to discover that it was an npc not designed to say anything! Simply put...an easy...non-elusive mud where a character can feel at home and experience the adventure that a mud is.
meepo64 is offline Reply With Quote
Old 03-26-2012, 09:52 AM #2
SnowTroll
Member
Join Date: Jan 2011
Posts: 183
SnowTroll will become famous soon enough
Re: Yet another looking for a mud request
This exact post appears about once a month, and I've never had a good answer for it. They usually begin by saying, without saying it: "I tried New Worlds (or a couple of the other muds like it), which is generally a pretty awesome mud, except for the fact that you have to spend a week auditioning for your character class and fit a certain mold to get it (that's what people really mean when they say they want a mud without or less reliant on "guilds"; they're just trying not to name the mud they tried), the fact that its crafting system is supremely limited, and the fact that figuring out some of the in game quests is more of a nightmarish matter of syntax and figuring out what to type than intelligently figuring out what to do." After the fourth or fifth post like that, one wonders whether the New Worlds people might consider making their quests/tasks more user-friendly to figure out, and adding more robust crafting features to the game. The whole auditioning to get into a guild thing is really that game's bread and butter. They're never changing that. But they could improve the other two things.
But I haven't found a good mud that answers a post like this yet. Maiden Desmodus is supposed to have a fairly developed crafting system, but I never got into the game and can't personally speak to any of its pros/cons, and a lot of things are/were in flux over there. I don't know what's going on with the Frogdice people, but if they ever resurrect Primordiax, it has a fairly developed crafting system and a very abundant and obvious quest/task system. Dark and Shattered Lands has a crafting system, but I found it kind of time consuming and tedious, and its quest system is more of the traditional Diku questmaster type system.
A lot of people really like the Iron Realms games, which do have crafting-type skill trees and in-game quests, but there's the obvious "pay-for-perks" model, which most people really don't have a problem with, but those games take it to an extreme, where by max level, you can't even learn all of your character class's skills without buying into the system.
SnowTroll is offline Reply With Quote
Old 03-26-2012, 02:31 PM #3
Nuku_v
New Member
Join Date: Nov 2010
Posts: 8
Nuku_v is on a distinguished road
Re: Yet another looking for a mud request
Flexible Survival(flexiblesurvival.com 2222) has all of that. Want to talk to someone, easy, talk (name), done! We have a detailed craft system that is NOT buried under piles of odd syntax(You can actually do it all from a web page, point and click).
Warning: Very adult.
Nuku_v is offline Reply With Quote
Old 03-26-2012, 04:15 PM #4
meepo64
New Member
Join Date: Dec 2011
Posts: 4
meepo64 is on a distinguished road
Re: Yet another looking for a mud request
Thank you for the fast reply! Yeah, I had tried out primordiax once, but stopped early on. I went back a few days ago only to find that I was unable to connect to their server. Now I know why!
I had played graphic mmorpgs for a few years, and really liked the idea of the player-formed guilds. This seems to be something nonexistent in muds....not sure why. I like being an adventurer, not a power-leveling member of an established guild. If later, I decide to join a player-formed guild, via an invite or whatever, that is my choice. It isn't as if my membership in a game-established guild is necessary if I hope to develop my characters skills and such. I also like the idea that I can learn whatever crafts I am interested in. It gives a player a chance to try out different crafts before deciding which ones they tend toward. Just seems like I must be asking too much
Muds are awesome for their reliance on a player's imagination to create the visuals and feelings of the game. I enjoy that challenge. I prefer the fantasy genre, but without the player killing, and I am not looking for an "adult only" slanted game. Just want to adventure, quest, craft and have fun!
meepo64 is offline Reply With Quote
Old 03-26-2012, 07:10 PM #5
camlorn
Member
Join Date: Aug 2011
Posts: 144
camlorn is on a distinguished road
Re: Yet another looking for a mud request
Well, there's 3 kingdoms, which I come back to a lot. Before I say anymore, I will warn that it has donations-for-ingame-perks, though many get by without them. They don't really add much in the way of power; they're just nice things like longer friend lists (50 is the default, I think). O, and eq doesn't save over boot.
So why does it fit: they do have crafting. It is complex, and will help with your survival. Essentially, crafting is an alternative to a bootrun, if you are familiar with the concept, and resources do save, even if the eq doesn't. They did a good job with it: cooking is free-form, without any predefined recipes, rangling is killing mobs to suck their essence/soul/whatever, and no one has yet figured out how exactly farming works, though it is possible to succeed at it if you have the patients for the failures. They also have guilds; on 3k, some require recruitment, but they have a sister mud called 3scapes which doesn't and has most of the same ones. WEven then, it's not like you have to apply; it's more of a tell so-and-so "I want to join your guild, can you recruit me?" and you're in. Very, very unique guilds; mages actually summon stuff to follow them around with a chance of it turning on you if you're not careful, bards actually have magical songs with lyrics that take multiple rounds to sing, and a whole bunch of other stuff including shapeshifters. O, and it has players and lots of them, so you don't know everyone right off the bat.
Others that fit what you want, and I hesitate to reccomend these two because they don't have active coders, but dark legacy beats everyone for crafting and project bob beats everyone for classless, so idk. Depends on if you care about changes/stability; the former can reliably be crashed by players (the method to do so is used in loo of a head admin to do reboots, remember what I said about inactive staff). The latter has barely active admin, but is stable enough to get along without them; that said, there was one serious bug where a character could only use tells
and it wasn't resolved when i left after two months...I left because of that, actually. Extremely fun, though, both of those.
Unfortunately, crafting and pve is rare. Batmud has it, and some other neet features, but you can't just jump into it; I know dark and shattered lands does, but again, it's a high level activity. Alter aeon does have most of the requirements you asked for, but only offers alchemy/poisons at last check.
For crafting in an rp environment that isn't awful, there is dartmud; it gets repetative fast, however.
Godwars2 has, among other things, a cool combat system and a small bit of crafting; it is completely pk, however, and has some other issues.
Try 7th plane. It has everything you asked for, including easy mob interaction and fully developed crafting.
Pick any coffeemud out there, and they probably kept the stock classes; the stock coffeemud classes are complete, which is unfortunate imho as it doesn't leave room for originality, but they do have crafting and it is definitely comprehensive. It is only recent that coffeemuds have been picking up, however.
Lensmoor has crafting, and it is very detailed and necessary, but I'm not qualified to talk about it in anything resembling a helpful capacity, mostly because i only played for a few weeks.
I honestly think I just covered almost every mud in existance with crafting worth talking about; does anyone know of any more? Tbh, I'm interested in this question too.
ps: easy quest interaction: Most muds don't have it. Of the above, only alter aeon has easy, simple, non-guess-the-magic-word talk command; you're not going to find that feature, at least not completely. A sign of a good builder, in my opinion, is getting a reaction to anything you try, so long as it is at least within the realm of possibility...I agree, guess-the-word games are annoying.
camlorn is offline Reply With Quote
Old 03-26-2012, 10:53 PM #6
realmsofvalor
New Member
realmsofvalor's Avatar
Join Date: Jul 2011
Posts: 22
realmsofvalor is on a distinguished road
Re: Yet another looking for a mud request
Hello meepo64 (and meepo65, meepo66 & meepo67 if divided you stand),
I'd like to take a moment to hit on some of the things you've been looking for in a MUD in regards to the game I work on, Arantha (arantha.net:4000). We are a comparatively new roleplay-required MUD that is always looking for players and helpers.
First, the bad: Our crafting system is not 'robust', in fact it is mostly non-existent. Though gem-crafting elements will be in-game shortly, weapon and other craft systems are largely absent; these have been skimped while many other areas of the game have much time and effort put into them. More than a few of these 'looking for a MUD' posts emphasize strong crafting systems, and I don't want to falsify what we offer. This is certainly something I want to build up in the future, and I would welcome discussion on how to do so and what folks find important and attractive in a crafting system.
Our quest system is something different from the usual autoquests that many games provide. I am interested in putting in some linear elements, but not to the excess that many games do. We rely on quests and roleplay spun by our Staff members, and usually run an event roughly once a week; this is an opportunity to not only loot and profit, risking life and limb, but also to show off your roleplay in front of an audience. Arantha's staff is very encouraging of exceptional roleplay and ready to reward where it is glimpsed.
There are guilds of various sorts, some established and populated by players, others in campaign and as of yet fleshed-out. This is an area where I have come to rely on players (with Staff aid) steering the organizations, with a flexible campaign background to get them started. Ultimately, it ain't about the establishment, it's the players that make things bloom and grow. If you see something you like, or don't, or feel is missing, or wish to bring to life, by all means, let's talk about it! Your ideas are just as much fodder for the world as ours.
Our setting is medieval fantasy with rules emulated from AD&D 2nd edition, we've got a great amount of areas (over 3,500 rooms EACH with unique description), and food, hey, plenty of that.. and there's plenty more we could have! Think we should have more chicken? Write some up, I'd be glad to plug in more chicken! 'Least you got it!
Our playerbase is not large enough to assume real difficulty in 'making your mark', as it were, and we at Arantha are all about the fun of the game. It's one of our rules, in fact, the most important one. The world is, outside of cities, unfortunately dangerous and there is the chance for some player-killing, but we restrict it to roleplay-requirements (would your character murder? what's the justification?). We are 'Adult' in that you must be 18 years of age to create an account, due to the sometimes-adult themes, text violence, and occasional curse words.
If you've great imagination, come by and check out our vibes, and see if Arantha works for you. In any event, have fun and best of luck on your search for a MUD to call home!
Our website: Arantha: The Realms of Valor
realmsofvalor is offline Reply With Quote
Old 03-27-2012, 02:38 AM #7
Dionae
Member
Join Date: Apr 2002
Location: Littleton, CO, US
Posts: 123
Dionae is on a distinguished road
Send a message via AIM to Dionae
Re: Yet another looking for a mud request
Hm, well, Geas does have guilds. The "occupational" guilds would be the sort that you are describing, as they have their own clear goals and values and ways that a character of that guild should act and things they stand for. But, in almost 3 years of playing, I've yet to join an occupational guild on any of my chars because they simply didn't fit my character. I made one character with the ambition of eventually joining one of the guilds, though I may end up joining a different one that is just coming into being through PC and wizard collaboration. It's true that joining an occupational guild gives you something to strive for, a purpose and goals, allies, as well as a set of skills that are limited to that guild. But I wouldn't say it's necessary to enjoying the game.
There are also crafting guilds, though currently the majority of them are steps in bookbinding. But there's also mining, fishing, gemcutting, and you can craft tents and arrows. Another set of guilds are the layman guilds, which include Alchemists, Scribes, and Skalds. These can each get minor magical benefits from potions, scrolls, and magic songs. While the Skalds are the least developed, the alchemy system involves plenty of opportunity to experiment and research unknown potions, and the Scribes' magic system is currently developing into a separate Mage guild. The layman guilds are looser and easier to join than the occupational guilds, and so they might be something to consider to keep you occupied without drawing you into unwanted conflict or having too many restrictions on your character.
Geas does have a ton of quests, which is something I've enjoyed. Some you can easily solve on your own, and some require assistance as they involve fighting tough monsters. It seemed like everywhere I went I uncovered a new quest, and there are still a number of them I've yet to solve. Usually asking an NPC for "help" will reveal whether there's something for you to do.
Anyway, check us out if you're so inclined.
Geas
geas.de port: 3333
Dionae is offline Reply With Quote
Old 03-27-2012, 11:24 AM #8
Will
Member
Join Date: Aug 2007
Posts: 90
Will is on a distinguished road
Re: Yet another looking for a mud request
Quote:
Originally Posted by meepo64 View Post
I have been playing muds for a few months now and have jumped around to a variety of them.
What I have been looking for is a mud that does not rely on guilds, has plenty of quests, and has a robust crafting system. I am not opposed to guilds that are formed among players as a means of solidarity and offering help and perks. I just don't prefer the muds where they force/encourage membership in an established guild, which, in turn, dictates quite a bit about your character's development. I enjoy exploring the intricacies of the land around, crafting items, food, etc. to help in survival and a means of commerce, in a non-pvp environment.
I also enjoy quests, and a mud where talking to an npc to see if a quest/task is available does not become a frustrating long process of scouring help files, asking players who won't give you a solid answer for fear of spoilers, just to discover that it was an npc not designed to say anything! Simply put...an easy...non-elusive mud where a character can feel at home and experience the adventure that a mud is.
Do you object to guilds if they don't dictate character direction?
Will is offline Reply With Quote
Old 03-27-2012, 04:57 PM #9
Realedazed
Member
Realedazed's Avatar
Join Date: May 2002
Location: AZ
Home MUD: Armageddon
Home MUD: Harshlands
Home MUD: DartMUD
Posts: 157
Realedazed is on a distinguished road
Send a message via AIM to Realedazed Send a message via Yahoo to Realedazed
Re: Yet another looking for a mud request
I feel you. The guild thing really gets annoying fast. Especially when you have to jump through a bunch of virtual hoops, talk to like 9 PCs (that may be on a totally different play schedule as you) just to get access to skills and/or status. It gets very annoying when the lack of guild skills and and status exclude you from some parts of the game.
I only like it when guilds or clans are more of a social group than a gatekeeper of required skills. In my opinion, only a few games do it for me.
In Armaggedon, your clan/guild doesn't give you any skills. However, they may make learning them easier. Also, they may provide a safe place to sleep (logout), access to clean water and food. As well as the RP benefits as contacts, events, etc. Plus, to get in, its all RP and some time a task: hunt this, steal this, con that guy, etc.
In Lusternia (and I thinking all of the other IRE games, since their guild structure seems the same), you get access to a few guild skills and they give you a check list of chores to do as a novice. I actually hate that check list, but if you are complete newbie, it helps you learn the game's story, survival, etc. I do hate the essays, though. But, there are tons of quests and the other players are not that strict with the well known or main city quest details. Also, there is crafting. You only get one, though. I'm only familiar with Lusternia's system, so I'm not sure about the rest. Lastly, I spent money in Lusternia. However, you can do other things for credits and buy them in game, too. It just really depends on your play style, wallet or both.
DartMud Is a cool game. You can learn almost every skill on your own, but its faster to get a teacher. There are other "shady" skills that MUST be learned from a teacher, though. Don't ask publicly about them either. There are quests to find, however you have to ask around in game for info on some of them. Also, as someone replied earlier, crafting is really repetitive. What I do is hang out with other crafters, work out my crafts while RPing. I think that's kinda cheesy though. Also, in my opinion, no one really sells anything other than quest rewards, so there's no real economy. Plus most players can make everything, so there is no supply and demand. Also, Everyone just cooks steaks to sell to the store to pay for rent on their inn rooms or castles.
All that aside, the details of crafting is amazing. There are so many materials to apply to the various crafts. You can make yourself a red silk cloak with black velvet stitching and cheetah fur lined hood, for example. I read in an old ad for the game that the cooking skill alone has about 300+ recipes (One reason why I hate that everyone always makes steaks and roasts!)
Realedazed is offline Reply With Quote
Old 03-28-2012, 02:57 PM #10
meepo64
New Member
Join Date: Dec 2011
Posts: 4
meepo64 is on a distinguished road
Re: Yet another looking for a mud request
Thanks to the many replies/help in my mud search! I will try some of the ones that have been recommended. Will have to let you know if i find one that fits! Thanks again
meepo64 is offline Reply With Quote
Old 04-01-2012, 10:32 AM #11
Newworlds
Legend
Newworlds's Avatar
Join Date: Aug 2007
Name: NewWorlds
Home MUD: New Worlds
Posts: 1,393
Newworlds will become famous soon enoughNewworlds will become famous soon enough
Re: Yet another looking for a mud request
Quote:
Originally Posted by meepo64 View Post
Thanks to the many replies/help in my mud search! I will try some of the ones that have been recommended. Will have to let you know if i find one that fits! Thanks again
For when you don't find that game that has incredible depth and feel I'll give you the reason for serious roleplaying of hard line Guilds and Quests that aren't giveaways by your fellow adventurers.
1. Guilds.
While I can appreciate independance and wanting to just be in a guild for a social group, I really do not see the point (in a roleplay enforced environment) to have guilds at all that have no rules or you can just join without any roleplay or requirements. Yes, the game should be fun and not tedius, however, if a game is so simplistic you can do anything with little effort the fun becomes short lived. As the old axiom says, "no pain no gain."
2. Quests.
Sort of the same issue here as above. If you can just learn the quest secrets from your fellow player, why have quests at all? "Hey bobby, just take this knife, cut the rope there, and then fish out those rubies! Yeah, like that, good job bobby!" That sort of thing happens on 90% of games and destroys the enjoyment of discovery (in my oppinion).
The reason the above two issues are the way they are on New Worlds Ateraan is because our playerbase enjoy mature, strong roleplaying and the style of the game breeds both.
Every player has an idea of how fun is acheaved and I don't hold the grand answer to that, I just wanted to give an alternative reason for some of your initial questions.
Enjoy the hunt!
Newworlds is offline Reply With Quote
Old 04-03-2012, 04:43 PM #12
meepo64
New Member
Join Date: Dec 2011
Posts: 4
meepo64 is on a distinguished road
Re: Yet another looking for a mud request
Well, have been looking around at a bunch of different muds. Have found one called "conquest" which, so far, is great! It has the simple questing with npcs and crafting. The big drawback is very few people are online at a given time I still want to keep playing and see what happens!
meepo64 is offline Reply With Quote
Old 04-07-2012, 03:09 PM #13
Bardicer
New Member
Join Date: Aug 2010
Posts: 3
Bardicer is on a distinguished road
Re: Yet another looking for a mud request
I would suggest checking out Lensmoor. There is a clan system, and it is COMPLETELY player driven. There are no set classes - if you have the skillcap you can learn everything except racial skills/spells.
Crafting system? In Lensmoor you mine ores and gems (gems are used for enchanting), metalwork the ores into metals, metalwork different metals together to make alloys (coal + iron = steel... copper and iron = bronze I believe, etc.) and create wearable/enchantable/detailable objects like weapons, armor, and jewelry. You can also collect herbs to create potions, salves, and pills. You can ALSO create casters, staves, and wands as well.
The quest system is pretty robust... you can do solo hack&slash quests (capture a mob, kill a mob, find an item, or find a mob and ask it a question pertaining to the game) or you can do solo crafting quests (gather this material, or craft this item and deliver it to that mob), OR you can do group quests which are hack&slash (kill a horde of x mob in y area, or kill x mob in y area that's a leader).
You can own shops, you can own houses, you can have pets, you can even CREATE pets once you learn beast fusion.
The ONLY drawback to Lensmoor right now is that the playerbase has dwindled down due to people getting sucked into real life. At one point there was an average of 60 people on at any given time with a peak of 150-175 people on at once...but over the years it's shrunk to an average of 10-15 people on at once and a peak of 25-40 people on.
There is no character approval process, RP isn't strictly enforced UNLESS you're PK (you have to have a valid reason to kill someone), and everything is pretty much in the hands of the players. It's been up since '97, and I've been playing since '99.
Bardicer is offline Reply With Quote
Reply
Thread Tools
Posting Rules
You may not post new threads
You may not post replies
You may not post attachments
You may not edit your posts
vB code is On
Smilies are On
[IMG] code is On
HTML code is Off
All times are GMT -4. The time now is 08:35 AM.
Powered by vBulletin® Version 3.6.7
Copyright ©2000 - 2018, Jelsoft Enterprises Ltd.
Style based on a design by Essilor
Copyright Top Mud Sites.com 2014
|
{
"url": "http://www.topmudsites.com/forums/showthread.php?s=0787a35528d1dab4aacc498afaa8acbd&t=1337&goto=nextoldest",
"source_domain": "www.topmudsites.com",
"snapshot_id": "crawl=CC-MAIN-2018-17",
"warc_metadata": {
"Content-Length": "95295",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:TDR2S7YTIWVBGWR6CLCBRHTVZF7UNRDP",
"WARC-Concurrent-To": "<urn:uuid:baa5b904-2590-459c-bf1c-c777a910e169>",
"WARC-Date": "2018-04-25T12:35:24Z",
"WARC-IP-Address": "209.133.212.238",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:LHDD3QRRAKQ7KF3VVCYKNEZOVQY5CMD6",
"WARC-Record-ID": "<urn:uuid:54fd9ba2-6369-4c40-ae1f-2fc639d54abd>",
"WARC-Target-URI": "http://www.topmudsites.com/forums/showthread.php?s=0787a35528d1dab4aacc498afaa8acbd&t=1337&goto=nextoldest",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:80836e81-7d75-4a20-92fd-6ac4c73343a0>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-141-249-121.ec2.internal\r\nsoftware: Nutch 1.6 (CC)\r\nisPartOf: CC-MAIN-2018-17\r\noperator: Common Crawl Admin\r\ndescription: Wide crawl of the web for April 2018\r\npublisher: Common Crawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
46,
139,
162,
163,
169,
171,
184,
214,
222,
233,
235,
255,
264,
299,
337,
338,
429,
430,
982,
983,
1396,
1434,
1464,
1474,
1481,
1483,
1503,
1514,
1555,
1597,
1598,
2712,
2713,
3346,
3347,
3706,
3746,
3776,
3783,
3794,
3796,
3816,
3825,
3859,
3901,
3902,
4153,
4154,
4175,
4212,
4242,
4250,
4261,
4263,
4283,
4292,
4327,
4369,
4370,
4563,
4564,
5244,
5245,
5545,
5583,
5613,
5621,
5628,
5630,
5650,
5661,
5696,
5738,
5739,
6062,
6063,
7220,
7221,
7792,
7918,
7919,
8223,
8224,
8328,
8329,
8470,
8471,
8580,
8581,
8890,
8891,
9081,
9082,
9251,
9252,
9644,
9682,
9712,
9726,
9737,
9739,
9762,
9764,
9784,
9794,
9835,
9877,
9878,
9947,
9948,
10195,
10196,
10794,
10795,
11321,
11322,
11877,
11878,
12213,
12214,
12778,
12779,
12954,
12955,
12997,
13041,
13071,
13078,
13085,
13087,
13107,
13135,
13146,
13180,
13213,
13255,
13256,
14036,
14037,
14843,
14844,
15217,
15218,
15262,
15263,
15268,
15287,
15324,
15354,
15359,
15366,
15368,
15388,
15398,
15430,
15472,
15473,
15480,
15519,
15610,
15611,
16163,
16164,
16577,
16644,
16679,
16709,
16720,
16727,
16729,
16749,
16751,
16771,
16784,
16805,
16826,
16844,
16855,
16893,
16969,
17011,
17012,
17363,
17364,
17511,
17512,
17849,
17850,
17851,
18610,
18611,
19373,
19374,
19749,
19790,
19821,
19829,
19840,
19842,
19862,
19871,
19906,
19948,
19949,
20119,
20157,
20188,
20198,
20205,
20207,
20226,
20228,
20248,
20264,
20285,
20298,
20379,
20421,
20422,
20429,
20468,
20638,
20837,
20838,
20849,
21296,
21297,
21308,
21656,
21657,
21830,
21831,
22002,
22003,
22019,
22059,
22090,
22098,
22109,
22111,
22131,
22140,
22175,
22217,
22218,
22502,
22540,
22571,
22580,
22591,
22593,
22613,
22622,
22658,
22700,
22701,
22906,
22907,
23346,
23347,
23750,
23751,
23863,
23864,
24204,
24205,
24456,
24495,
24501,
24502,
24503,
24516,
24517,
24518,
24532,
24561,
24586,
24615,
24643,
24644,
24658,
24673,
24690,
24707,
24708,
24756,
24757,
24758,
24794,
24843,
24878
],
"line_end_idx": [
46,
139,
162,
163,
169,
171,
184,
214,
222,
233,
235,
255,
264,
299,
337,
338,
429,
430,
982,
983,
1396,
1434,
1464,
1474,
1481,
1483,
1503,
1514,
1555,
1597,
1598,
2712,
2713,
3346,
3347,
3706,
3746,
3776,
3783,
3794,
3796,
3816,
3825,
3859,
3901,
3902,
4153,
4154,
4175,
4212,
4242,
4250,
4261,
4263,
4283,
4292,
4327,
4369,
4370,
4563,
4564,
5244,
5245,
5545,
5583,
5613,
5621,
5628,
5630,
5650,
5661,
5696,
5738,
5739,
6062,
6063,
7220,
7221,
7792,
7918,
7919,
8223,
8224,
8328,
8329,
8470,
8471,
8580,
8581,
8890,
8891,
9081,
9082,
9251,
9252,
9644,
9682,
9712,
9726,
9737,
9739,
9762,
9764,
9784,
9794,
9835,
9877,
9878,
9947,
9948,
10195,
10196,
10794,
10795,
11321,
11322,
11877,
11878,
12213,
12214,
12778,
12779,
12954,
12955,
12997,
13041,
13071,
13078,
13085,
13087,
13107,
13135,
13146,
13180,
13213,
13255,
13256,
14036,
14037,
14843,
14844,
15217,
15218,
15262,
15263,
15268,
15287,
15324,
15354,
15359,
15366,
15368,
15388,
15398,
15430,
15472,
15473,
15480,
15519,
15610,
15611,
16163,
16164,
16577,
16644,
16679,
16709,
16720,
16727,
16729,
16749,
16751,
16771,
16784,
16805,
16826,
16844,
16855,
16893,
16969,
17011,
17012,
17363,
17364,
17511,
17512,
17849,
17850,
17851,
18610,
18611,
19373,
19374,
19749,
19790,
19821,
19829,
19840,
19842,
19862,
19871,
19906,
19948,
19949,
20119,
20157,
20188,
20198,
20205,
20207,
20226,
20228,
20248,
20264,
20285,
20298,
20379,
20421,
20422,
20429,
20468,
20638,
20837,
20838,
20849,
21296,
21297,
21308,
21656,
21657,
21830,
21831,
22002,
22003,
22019,
22059,
22090,
22098,
22109,
22111,
22131,
22140,
22175,
22217,
22218,
22502,
22540,
22571,
22580,
22591,
22593,
22613,
22622,
22658,
22700,
22701,
22906,
22907,
23346,
23347,
23750,
23751,
23863,
23864,
24204,
24205,
24456,
24495,
24501,
24502,
24503,
24516,
24517,
24518,
24532,
24561,
24586,
24615,
24643,
24644,
24658,
24673,
24690,
24707,
24708,
24756,
24757,
24758,
24794,
24843,
24878,
24910
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 24910,
"ccnet_original_nlines": 291,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 1,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.4369180202484131,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.025378860533237457,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.17947782576084137,
"rps_doc_frac_unique_words": 0.2711864411830902,
"rps_doc_mean_word_length": 4.389830589294434,
"rps_doc_num_sentences": 220,
"rps_doc_symbol_to_word_ratio": 0.004199380055069923,
"rps_doc_unigram_entropy": 6.012010097503662,
"rps_doc_word_count": 4425,
"rps_doc_frac_chars_dupe_10grams": 0.14682111144065857,
"rps_doc_frac_chars_dupe_5grams": 0.17812098562717438,
"rps_doc_frac_chars_dupe_6grams": 0.17271557450294495,
"rps_doc_frac_chars_dupe_7grams": 0.1700386106967926,
"rps_doc_frac_chars_dupe_8grams": 0.15613900125026703,
"rps_doc_frac_chars_dupe_9grams": 0.14862291514873505,
"rps_doc_frac_chars_top_2gram": 0.0047361599281430244,
"rps_doc_frac_chars_top_3gram": 0.0054054101929068565,
"rps_doc_frac_chars_top_4gram": 0.010090090334415436,
"rps_doc_books_importance": -2578.09033203125,
"rps_doc_books_importance_length_correction": -2578.09033203125,
"rps_doc_openwebtext_importance": -1819.611328125,
"rps_doc_openwebtext_importance_length_correction": -1819.611328125,
"rps_doc_wikipedia_importance": -1361.935546875,
"rps_doc_wikipedia_importance_length_correction": -1361.935546875
},
"fasttext": {
"dclm": 0.020925279706716537,
"english": 0.969328761100769,
"fineweb_edu_approx": 1.0984286069869995,
"eai_general_math": 0.02492987923324108,
"eai_open_web_math": 0.21963751316070557,
"eai_web_code": 0.0008698099991306663
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.656",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "794.8",
"labels": {
"level_1": "Arts",
"level_2": "Amusements and Recreation",
"level_3": ""
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "5",
"label": "Evaluate"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "2",
"label": "Click Here References"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "5",
"label": "Comment Section"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "6",
"label": "Not Applicable/Indeterminate"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "1",
"label": "General Audience"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-1,187,365,299,322,212,000
|
GSP
Quick Navigator
Search Site
Unix VPS
A - Starter
B - Basic
C - Preferred
D - Commercial
MPS - Dedicated
Previous VPSs
* Sign Up! *
Support
Contact Us
Online Help
Handbooks
Domain Status
Man Pages
FAQ
Virtual Servers
Pricing
Billing
Technical
Network
Facilities
Connectivity
Topology Map
Miscellaneous
Server Agreement
Year 2038
Credits
USA Flag
Man Pages
Manual Reference Pages - MIDIDEL (n)
NAME
mididelete - tclmidi command to delete an event or events in a MIDI song
CONTENTS
Synopsis
Description
Return Values
See Also
Author
SYNOPSIS
mididelete MidiID track event
mididelete MidiID track "range" start end
DESCRIPTION
mididelete is a tclmidi(1) command that deletes one or more events from a specified track in a MIDI song. The first argument is a MIDI song descriptor as returned by midimake(n) or midiread(n). The second argument is the track in the MIDI song. In the first form, the third argument is a specific event to remove. For formatting of events, see midievents(n).
In the second form, the third argument is the string "range". The fourth argument is then the start time of events to be delete and the last argument is the end time of the range. All events starting at time start up to but not including events at time end are then deleted.
RETURN VALUES
mididelete returns a 1 if the event or events were successfully removed, or 0 if, in the first case, the event could not be found.
SEE ALSO
tclmidi(1), midiread(n), midimake(n), midiput(n), midievents(n)
AUTHOR
Mike Durian - durian@boogie.com
Search for or go to Top of page | Section n | Main Index
Powered by GSP Visit the GSP FreeBSD Man Page Interface.
Output converted with manServer 1.07.
|
{
"url": "http://www.gsp.com/cgi-bin/man.cgi?section=n&topic=mididel",
"source_domain": "www.gsp.com",
"snapshot_id": "crawl=CC-MAIN-2018-26",
"warc_metadata": {
"Content-Length": "8224",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:ZZXHJM3MTEE6PS6J5BHNUJJENRS3XN5Y",
"WARC-Concurrent-To": "<urn:uuid:98d3fbac-5fd0-4aa8-bef6-fd18c60ce29b>",
"WARC-Date": "2018-06-25T07:33:25Z",
"WARC-IP-Address": "52.202.27.192",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:3XR3RAZEPSTGXJAPJS67GSE2TNF4YVHP",
"WARC-Record-ID": "<urn:uuid:44ca7c13-0508-49e0-9e04-523d7522cca5>",
"WARC-Target-URI": "http://www.gsp.com/cgi-bin/man.cgi?section=n&topic=mididel",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:618eba28-c97c-453e-8511-e2df1846fd64>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-154-202-165.ec2.internal\r\nsoftware: Nutch 1.6 (CC)\r\nisPartOf: CC-MAIN-2018-26\r\noperator: Common Crawl Admin\r\ndescription: Wide crawl of the web for June 2018\r\npublisher: Common Crawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
1,
5,
21,
22,
34,
35,
44,
56,
66,
80,
95,
111,
125,
138,
139,
147,
158,
170,
180,
194,
204,
205,
209,
225,
233,
241,
251,
252,
260,
271,
284,
297,
298,
312,
329,
339,
347,
349,
350,
359,
360,
362,
363,
365,
366,
376,
377,
378,
417,
418,
423,
424,
497,
498,
507,
508,
517,
529,
543,
552,
559,
560,
569,
570,
600,
642,
643,
655,
656,
1018,
1019,
1294,
1295,
1309,
1310,
1441,
1442,
1451,
1452,
1516,
1517,
1524,
1525,
1557,
1619,
1620,
1621,
1678
],
"line_end_idx": [
1,
5,
21,
22,
34,
35,
44,
56,
66,
80,
95,
111,
125,
138,
139,
147,
158,
170,
180,
194,
204,
205,
209,
225,
233,
241,
251,
252,
260,
271,
284,
297,
298,
312,
329,
339,
347,
349,
350,
359,
360,
362,
363,
365,
366,
376,
377,
378,
417,
418,
423,
424,
497,
498,
507,
508,
517,
529,
543,
552,
559,
560,
569,
570,
600,
642,
643,
655,
656,
1018,
1019,
1294,
1295,
1309,
1310,
1441,
1442,
1451,
1452,
1516,
1517,
1524,
1525,
1557,
1619,
1620,
1621,
1678,
1715
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 1715,
"ccnet_original_nlines": 88,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.2818991243839264,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.07418397814035416,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.18100890517234802,
"rps_doc_frac_unique_words": 0.553505539894104,
"rps_doc_mean_word_length": 4.892989158630371,
"rps_doc_num_sentences": 14,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.70241117477417,
"rps_doc_word_count": 271,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.033182501792907715,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.04524886980652809,
"rps_doc_frac_chars_top_3gram": 0.020361989736557007,
"rps_doc_frac_chars_top_4gram": 0.016591250896453857,
"rps_doc_books_importance": -150.8784942626953,
"rps_doc_books_importance_length_correction": -139.57003784179688,
"rps_doc_openwebtext_importance": -108.68964385986328,
"rps_doc_openwebtext_importance_length_correction": -108.68964385986328,
"rps_doc_wikipedia_importance": -81.23188781738281,
"rps_doc_wikipedia_importance_length_correction": -73.19554901123047
},
"fasttext": {
"dclm": 0.024275900796055794,
"english": 0.7702866196632385,
"fineweb_edu_approx": 1.5118929147720337,
"eai_general_math": 0.0014837400522083044,
"eai_open_web_math": 0.533105194568634,
"eai_web_code": 0.0011008400470018387
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.4",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "781.7",
"labels": {
"level_1": "Arts",
"level_2": "Music",
"level_3": "Music theory"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "1",
"label": "Factual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "10",
"label": "Knowledge Article"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "1",
"label": "No Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-2,010,388,227,028,999,700
|
[macOS] Set Finder Tags
How-to guides, frequently asked questions, not-so-obvious features, etc
Post Reply
User avatar
rednoah
The Source
Posts: 21345
Joined: 16 Nov 2011, 08:59
[macOS] Set Finder Tags
Post by rednoah »
The Set Finder Tags allows you to add a series of tags to your movie and episode files to make them more accessible in Finder.
e.g. export Finder tags for existing files:
Code: Select all
filebot -find /input --apply finder
Image
By default, the list of tags for each file is generated by the following format expression:
Code: Select all
FileBot
{ movie; 'Movie' }
{ episode; anime ? 'Anime' : 'TV Show' }
{ movie; genre }
{ movie; '★' * (rating / 2).round() }
{ y }
{ hd == 'UHD' && hdr ? 'HDR 4K' : null }
:idea: The default tags defined by the format above are experimental and subject to change. Please provide feedback if you would like to see different tags by default.
:idea: Please read the FAQ and How to Request Help.
Post Reply
|
{
"url": "https://www.filebot.net/forums/viewtopic.php?t=12654",
"source_domain": "www.filebot.net",
"snapshot_id": "crawl=CC-MAIN-2022-49",
"warc_metadata": {
"Content-Length": "22280",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:QERZ7AOJHZCJTK36MY6WI6UAHVZDEGXI",
"WARC-Concurrent-To": "<urn:uuid:6900e6a0-896a-4574-a527-1233707a46ee>",
"WARC-Date": "2022-12-04T05:15:56Z",
"WARC-IP-Address": "104.21.79.38",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:NDIFZE43CDNAGBNEPYUPNLNWABQV2BZL",
"WARC-Record-ID": "<urn:uuid:5e0c7e8a-73c6-418b-85f8-58e1dd840a80>",
"WARC-Target-URI": "https://www.filebot.net/forums/viewtopic.php?t=12654",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:63537403-4288-4f51-a96b-2344160bc394>"
},
"warc_info": "isPartOf: CC-MAIN-2022-49\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for November/December 2022\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-8\r\nsoftware: Apache Nutch 1.19 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.4-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
24,
25,
97,
108,
120,
128,
139,
152,
179,
180,
204,
205,
223,
224,
351,
352,
353,
397,
398,
415,
416,
452,
453,
459,
460,
461,
553,
554,
571,
572,
580,
599,
640,
657,
695,
701,
742,
743,
744,
912,
964
],
"line_end_idx": [
24,
25,
97,
108,
120,
128,
139,
152,
179,
180,
204,
205,
223,
224,
351,
352,
353,
397,
398,
415,
416,
452,
453,
459,
460,
461,
553,
554,
571,
572,
580,
599,
640,
657,
695,
701,
742,
743,
744,
912,
964,
974
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 974,
"ccnet_original_nlines": 41,
"rps_doc_curly_bracket": 0.012320330366492271,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.208695650100708,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.021739130839705467,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.33478260040283203,
"rps_doc_frac_unique_words": 0.6387096643447876,
"rps_doc_mean_word_length": 4.574193477630615,
"rps_doc_num_sentences": 10,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.3685688972473145,
"rps_doc_word_count": 155,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.05641749128699303,
"rps_doc_frac_chars_top_3gram": 0.055007051676511765,
"rps_doc_frac_chars_top_4gram": 0.050775740295648575,
"rps_doc_books_importance": -102.85018157958984,
"rps_doc_books_importance_length_correction": -102.85018157958984,
"rps_doc_openwebtext_importance": -59.10197067260742,
"rps_doc_openwebtext_importance_length_correction": -45.30230712890625,
"rps_doc_wikipedia_importance": -40.15896224975586,
"rps_doc_wikipedia_importance_length_correction": -40.15896224975586
},
"fasttext": {
"dclm": 0.07451785355806351,
"english": 0.7500449419021606,
"fineweb_edu_approx": 1.274334192276001,
"eai_general_math": 0.003959599882364273,
"eai_open_web_math": 0.06603968143463135,
"eai_web_code": -0.0000014299999975264654
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.467",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.67",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "5",
"label": "Social/Forum"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "4",
"label": "Missing Images or Figures"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "23",
"label": "Tutorial"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
2,159,561,755,191,257,000
|
SQL Clone
SQLServerCentral is supported by Redgate
Log in :: Register :: Not logged in
BULK INSERT failing.
BULK INSERT failing.
Author
Message
Jamie Ashton
Jamie Ashton
SSC Rookie
SSC Rookie (43 reputation)SSC Rookie (43 reputation)SSC Rookie (43 reputation)SSC Rookie (43 reputation)SSC Rookie (43 reputation)SSC Rookie (43 reputation)SSC Rookie (43 reputation)SSC Rookie (43 reputation)
Group: General Forum Members
Points: 43 Visits: 147
Hello,
I have a situation where I am trying to do a bulk insert of a file that's on a network share. It's failing with:
Cannot bulk load because the file "\\Server\Folder\File" could not be opened. Operating system error code 5 (failed to retrieve text for this error. Reason: 15105).
What I think is odd though is that use of xp_FileExist confirms that that the file exists and the SQL Server can see it.
The remote folder has permissions for "Everyone". Is there an internal setting in SQL Server that has been set to prevent me doing this? It's a new server and so this has never been done before. But it worked fine in pre-production, on a different server.
Hope you can help.
J
Cadavre
Cadavre
Hall of Fame
Hall of Fame (3.9K reputation)Hall of Fame (3.9K reputation)Hall of Fame (3.9K reputation)Hall of Fame (3.9K reputation)Hall of Fame (3.9K reputation)Hall of Fame (3.9K reputation)Hall of Fame (3.9K reputation)Hall of Fame (3.9K reputation)
Group: General Forum Members
Points: 3880 Visits: 8472
Jamie Ashton (2/3/2012)
Hello,
I have a situation where I am trying to do a bulk insert of a file that's on a network share. It's failing with:
Cannot bulk load because the file "\\Server\Folder\File" could not be opened. Operating system error code 5 (failed to retrieve text for this error. Reason: 15105).
What I think is odd though is that use of xp_FileExist confirms that that the file exists and the SQL Server can see it.
The remote folder has permissions for "Everyone". Is there an internal setting in SQL Server that has been set to prevent me doing this? It's a new server and so this has never been done before. But it worked fine in pre-production, on a different server.
Hope you can help.
J
Error code 5 is permissions, so it might be worth checking that whatever account your SQL Server runs under has permission. Check the account used by the pre-production server and see if it's using the same.
Forever trying to learn
For better, quicker answers on T-SQL questions, click on the following...
http://www.sqlservercentral.com/articles/Best+Practices/61537/
For better, quicker answers on SQL Server performance related questions, click on the following...
http://www.sqlservercentral.com/articles/SQLServerCentral/66909/
If you litter your database queries with nolock query hints, are you aware of the side effects?
Try reading a few of these links...
(*) Missing rows with nolock
(*) Allocation order scans with nolock
(*) Consistency issues with nolock
(*) Transient Corruption Errors in SQL Server error log caused by nolock
(*) Dirty reads, read errors, reading rows twice and missing rows with nolock
Craig Wilkinson - Software Engineer
LinkedIn
derek.colley
derek.colley
SSC Eights!
SSC Eights! (868 reputation)SSC Eights! (868 reputation)SSC Eights! (868 reputation)SSC Eights! (868 reputation)SSC Eights! (868 reputation)SSC Eights! (868 reputation)SSC Eights! (868 reputation)SSC Eights! (868 reputation)
Group: General Forum Members
Points: 868 Visits: 603
Hi Jamie
I faced a similar situation not too long ago trying to do the exact same thing. I don't have a verifiable link but from experience, I've found SQL Server in general and SSIS packages in particular DO NOT get on with network shares at all.
You'll need to put the input file on a local drive for this to work. Don't forget about your BULK INSERT options, too - make sure they're set for the type of file you're using.
---
Note to developers:
CAST(SUBSTRING(CAST(FLOOR(NULLIF(ISNULL(COALESCE(1,NULL),NULL),NULL)) AS CHAR(1)),1,1) AS INT) == 1
So why complicate your code AND MAKE MY JOB HARDER??!Crazy
Want to get the best help? Click here http://www.sqlservercentral.com/articles/Best+Practices/61537/ (Jeff Moden)
My blog: http://uksqldba.blogspot.com
Visit http://www.DerekColley.co.uk to find out more about me.
Jamie Ashton
Jamie Ashton
SSC Rookie
SSC Rookie (43 reputation)SSC Rookie (43 reputation)SSC Rookie (43 reputation)SSC Rookie (43 reputation)SSC Rookie (43 reputation)SSC Rookie (43 reputation)SSC Rookie (43 reputation)SSC Rookie (43 reputation)
Group: General Forum Members
Points: 43 Visits: 147
Thanks both for your speedy answers!
Firstly the permissions... surely "Everyone" would encompass the SQL Server account?
And yes - I'd love to have the file locally - but it's impossible in this situation.
Don't you think it's odd that XP_FileExist can see it yet BULK INSERT fails?
Or are separate accounts involved?
J
derek.colley
derek.colley
SSC Eights!
SSC Eights! (868 reputation)SSC Eights! (868 reputation)SSC Eights! (868 reputation)SSC Eights! (868 reputation)SSC Eights! (868 reputation)SSC Eights! (868 reputation)SSC Eights! (868 reputation)SSC Eights! (868 reputation)
Group: General Forum Members
Points: 868 Visits: 603
I think it's got to be something to do with accounts. Maybe grant the SQL Server accounts explicit permissions on the network share. In terms of the XP call working, I suspect that internally it's using something like the Windows COM objects or some other Windows API which is returning a result (as it would do if you e.g. browsed a normal window).
A quick bit of Googling has found this which might be of help:
1) The SQL Server services, on the Server containing the instance of SQL Server, must be running under a domain-level account (e.g. A Domain Administrator account). This is accomplished by changing the "Log On" properties for the services named "MSSQLSERVER" and "SQLSERVERAGENT" on the server running SQL Server (not your local instance). When you have completed changing the log on information for these 2 services, you will need to restart the "MSSQLSERVER" service on that server. Note that this will ask if you want to restart the "SQLSERVERAGENT" as well - Answer: Yes.
2) The SQL Server service account must have FULL CONTROL rights to the file system folder and to the share. That means you need to have a shared location in which the logon account you specified in 1 (above) has full control rights.
3) The file share should only be accessed via UNC name. Mapped drives may not be consistently visible to the SQL Service.
4) You cannot specify the path by using the browse ellipses (...). You must type the fully qualified path into the text box as:
file://ComputerName/ShareDirectoryWithRightsForDomain-levelAccountUsed/NameofFile.Extension
Additional Notes:
When creating or restoring backups on a network share, a significant increase in network traffic may result. You should ensure that your network can handle this without causing poor performance for other systems or end users. It may also benefit you to establish a dedicated physical network connection between your database server and your backup file host. Once the SQL Server instance is configured, you can use your local Enterprise Manager to create or restore a database backup that resides on a network device other than the device your instance of SQL Server is running on.
(from http://www.fmsinc.com/free/NewTips/SQL/SQLtip9.asp)
I know this relates to SQL Server 2000 but I suspect it's right.
---
Note to developers:
CAST(SUBSTRING(CAST(FLOOR(NULLIF(ISNULL(COALESCE(1,NULL),NULL),NULL)) AS CHAR(1)),1,1) AS INT) == 1
So why complicate your code AND MAKE MY JOB HARDER??!Crazy
Want to get the best help? Click here http://www.sqlservercentral.com/articles/Best+Practices/61537/ (Jeff Moden)
My blog: http://uksqldba.blogspot.com
Visit http://www.DerekColley.co.uk to find out more about me.
Jamie Ashton
Jamie Ashton
SSC Rookie
SSC Rookie (43 reputation)SSC Rookie (43 reputation)SSC Rookie (43 reputation)SSC Rookie (43 reputation)SSC Rookie (43 reputation)SSC Rookie (43 reputation)SSC Rookie (43 reputation)SSC Rookie (43 reputation)
Group: General Forum Members
Points: 43 Visits: 147
Thanks all for your help on this one.
My research indicates numerous possible causes, but in this instance, it looks to be a permissions issue going across domains.
J
timexist
timexist
Valued Member
Valued Member (54 reputation)Valued Member (54 reputation)Valued Member (54 reputation)Valued Member (54 reputation)Valued Member (54 reputation)Valued Member (54 reputation)Valued Member (54 reputation)Valued Member (54 reputation)
Group: General Forum Members
Points: 54 Visits: 60
I just solved this issue.
two ways,
1, remote desktop to sql server do bulk insert there.
2, or you can use sql authentication to login.
have fun
FortyEightK
FortyEightK
SSC Journeyman
SSC Journeyman (82 reputation)SSC Journeyman (82 reputation)SSC Journeyman (82 reputation)SSC Journeyman (82 reputation)SSC Journeyman (82 reputation)SSC Journeyman (82 reputation)SSC Journeyman (82 reputation)SSC Journeyman (82 reputation)
Group: General Forum Members
Points: 82 Visits: 437
Bump!
Just thought I'd add my two-penneth as I was getting this exact error today and this was the first post I found on a search.
The BULK INSERT is performed from a stored procedure, specifically looking for a file in a local path. My problem wasn't permissions, some f**kwit decided it was a good idea to rename the folder!
kevaburg
kevaburg
SSCommitted
SSCommitted (1.6K reputation)SSCommitted (1.6K reputation)SSCommitted (1.6K reputation)SSCommitted (1.6K reputation)SSCommitted (1.6K reputation)SSCommitted (1.6K reputation)SSCommitted (1.6K reputation)SSCommitted (1.6K reputation)
Group: General Forum Members
Points: 1577 Visits: 988
FortyEightK (5/23/2013)
Bump!
Just thought I'd add my two-penneth as I was getting this exact error today and this was the first post I found on a search.
The BULK INSERT is performed from a stored procedure, specifically looking for a file in a local path. My problem wasn't permissions, some f**kwit decided it was a good idea to rename the folder!
ROTFL! Sounds like the solution wasn't that technical after all! :-D
I don't understand why XP_FILELIST didn't pick up on the change though....
Go
Permissions
You can't post new topics.
You can't post topic replies.
You can't post new polls.
You can't post replies to polls.
You can't edit your own topics.
You can't delete your own topics.
You can't edit other topics.
You can't delete other topics.
You can't edit your own posts.
You can't edit other posts.
You can't delete your own posts.
You can't delete other posts.
You can't post events.
You can't edit your own events.
You can't edit other events.
You can't delete your own events.
You can't delete other events.
You can't send private messages.
You can't send emails.
You can read topics.
You can't vote in polls.
You can't upload attachments.
You can download attachments.
You can't post HTML code.
You can't edit HTML code.
You can't post IFCode.
You can't post JavaScript.
You can post emoticons.
You can't post or upload images.
Select a forum
SQLServerCentral
Search
|
{
"url": "https://www.sqlservercentral.com/Forums/Topic1246339-391-1.aspx",
"source_domain": "www.sqlservercentral.com",
"snapshot_id": "crawl=CC-MAIN-2017-17",
"warc_metadata": {
"Content-Length": "263859",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:CELVWXMBLAFCP2J6K5L6ZCQU3XLSXT5M",
"WARC-Concurrent-To": "<urn:uuid:129e7123-2297-4951-9b20-007102bb17e9>",
"WARC-Date": "2017-04-25T05:52:41Z",
"WARC-IP-Address": "162.13.37.189",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:BWGGRJCTYT6CKSSIP6HZA52JOIZKBQWH",
"WARC-Record-ID": "<urn:uuid:b93c104b-01dd-4db1-baa7-c462492fb89b>",
"WARC-Target-URI": "https://www.sqlservercentral.com/Forums/Topic1246339-391-1.aspx",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:b7952c57-b0ef-4830-9876-28afb5206f2c>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-145-167-34.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2017-17\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web for April 2017\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
10,
51,
53,
93,
95,
97,
99,
100,
101,
122,
123,
124,
145,
146,
153,
161,
174,
187,
198,
407,
408,
437,
460,
467,
468,
581,
582,
747,
748,
869,
870,
1126,
1127,
1146,
1147,
1149,
1157,
1165,
1178,
1419,
1420,
1449,
1475,
1499,
1506,
1507,
1620,
1621,
1786,
1787,
1908,
1909,
2165,
2166,
2185,
2186,
2188,
2189,
2190,
2398,
2399,
2400,
2424,
2425,
2499,
2562,
2563,
2662,
2727,
2728,
2729,
2730,
2826,
2862,
2863,
2892,
2931,
2966,
3039,
3117,
3118,
3119,
3155,
3164,
3177,
3190,
3202,
3427,
3428,
3457,
3481,
3490,
3491,
3730,
3731,
3908,
3909,
3913,
3914,
3934,
4034,
4093,
4094,
4208,
4246,
4308,
4309,
4322,
4335,
4346,
4555,
4556,
4585,
4608,
4645,
4646,
4731,
4732,
4817,
4818,
4895,
4896,
4931,
4932,
4934,
4947,
4960,
4972,
5197,
5198,
5227,
5251,
5601,
5602,
5665,
5666,
5667,
6243,
6244,
6477,
6478,
6600,
6601,
6729,
6730,
6822,
6823,
6824,
6825,
6843,
7425,
7426,
7427,
7428,
7486,
7487,
7552,
7553,
7557,
7558,
7578,
7678,
7737,
7738,
7852,
7890,
7952,
7953,
7966,
7979,
7990,
8199,
8200,
8229,
8252,
8290,
8291,
8418,
8419,
8421,
8430,
8439,
8453,
8686,
8687,
8716,
8738,
8764,
8765,
8775,
8776,
8830,
8831,
8878,
8879,
8888,
8900,
8912,
8927,
9168,
9169,
9198,
9221,
9227,
9228,
9353,
9354,
9550,
9559,
9568,
9580,
9813,
9814,
9843,
9868,
9892,
9898,
9899,
10024,
10025,
10221,
10222,
10223,
10292,
10293,
10368,
10371,
10372,
10373,
10385,
10386,
10413,
10443,
10469,
10502,
10534,
10568,
10597,
10628,
10659,
10687,
10720,
10750,
10773,
10805,
10834,
10868,
10899,
10932,
10955,
10976,
11001,
11031,
11061,
11087,
11113,
11136,
11163,
11187,
11220,
11221,
11236,
11237,
11238,
11239,
11240,
11241,
11242,
11243,
11244,
11245,
11246,
11247,
11248,
11249,
11250,
11251,
11252,
11253,
11254,
11255,
11256,
11257,
11258,
11259,
11260,
11261,
11262,
11263,
11264,
11265,
11266,
11267,
11268,
11269,
11270,
11271,
11272,
11273,
11274,
11275,
11276,
11277,
11278,
11279,
11280,
11281,
11282,
11283,
11284,
11285,
11286,
11287,
11288,
11289,
11290,
11291,
11292,
11293,
11294,
11295,
11296,
11297,
11298,
11299,
11300,
11301,
11302,
11303,
11304,
11305,
11306,
11307,
11308,
11309,
11310,
11311,
11312,
11313,
11314,
11315,
11316,
11317,
11318,
11319,
11320,
11321,
11322,
11323,
11324,
11325,
11326,
11327,
11328,
11329,
11330,
11331,
11332,
11333,
11334,
11335,
11336,
11337,
11338,
11339,
11340,
11341,
11342,
11343,
11344,
11345,
11346,
11347,
11348,
11349,
11350,
11351,
11352,
11353,
11354,
11355,
11356,
11357,
11358,
11359,
11360,
11361,
11362,
11363,
11364,
11365,
11366,
11367,
11368,
11369,
11370,
11371,
11372,
11373,
11374,
11375,
11376,
11377,
11378,
11379,
11380,
11381,
11382,
11383,
11384,
11385,
11386,
11387,
11388,
11389,
11390,
11391,
11392,
11393,
11394,
11395,
11396,
11397,
11414,
11415,
11416,
11423,
11424,
11426
],
"line_end_idx": [
10,
51,
53,
93,
95,
97,
99,
100,
101,
122,
123,
124,
145,
146,
153,
161,
174,
187,
198,
407,
408,
437,
460,
467,
468,
581,
582,
747,
748,
869,
870,
1126,
1127,
1146,
1147,
1149,
1157,
1165,
1178,
1419,
1420,
1449,
1475,
1499,
1506,
1507,
1620,
1621,
1786,
1787,
1908,
1909,
2165,
2166,
2185,
2186,
2188,
2189,
2190,
2398,
2399,
2400,
2424,
2425,
2499,
2562,
2563,
2662,
2727,
2728,
2729,
2730,
2826,
2862,
2863,
2892,
2931,
2966,
3039,
3117,
3118,
3119,
3155,
3164,
3177,
3190,
3202,
3427,
3428,
3457,
3481,
3490,
3491,
3730,
3731,
3908,
3909,
3913,
3914,
3934,
4034,
4093,
4094,
4208,
4246,
4308,
4309,
4322,
4335,
4346,
4555,
4556,
4585,
4608,
4645,
4646,
4731,
4732,
4817,
4818,
4895,
4896,
4931,
4932,
4934,
4947,
4960,
4972,
5197,
5198,
5227,
5251,
5601,
5602,
5665,
5666,
5667,
6243,
6244,
6477,
6478,
6600,
6601,
6729,
6730,
6822,
6823,
6824,
6825,
6843,
7425,
7426,
7427,
7428,
7486,
7487,
7552,
7553,
7557,
7558,
7578,
7678,
7737,
7738,
7852,
7890,
7952,
7953,
7966,
7979,
7990,
8199,
8200,
8229,
8252,
8290,
8291,
8418,
8419,
8421,
8430,
8439,
8453,
8686,
8687,
8716,
8738,
8764,
8765,
8775,
8776,
8830,
8831,
8878,
8879,
8888,
8900,
8912,
8927,
9168,
9169,
9198,
9221,
9227,
9228,
9353,
9354,
9550,
9559,
9568,
9580,
9813,
9814,
9843,
9868,
9892,
9898,
9899,
10024,
10025,
10221,
10222,
10223,
10292,
10293,
10368,
10371,
10372,
10373,
10385,
10386,
10413,
10443,
10469,
10502,
10534,
10568,
10597,
10628,
10659,
10687,
10720,
10750,
10773,
10805,
10834,
10868,
10899,
10932,
10955,
10976,
11001,
11031,
11061,
11087,
11113,
11136,
11163,
11187,
11220,
11221,
11236,
11237,
11238,
11239,
11240,
11241,
11242,
11243,
11244,
11245,
11246,
11247,
11248,
11249,
11250,
11251,
11252,
11253,
11254,
11255,
11256,
11257,
11258,
11259,
11260,
11261,
11262,
11263,
11264,
11265,
11266,
11267,
11268,
11269,
11270,
11271,
11272,
11273,
11274,
11275,
11276,
11277,
11278,
11279,
11280,
11281,
11282,
11283,
11284,
11285,
11286,
11287,
11288,
11289,
11290,
11291,
11292,
11293,
11294,
11295,
11296,
11297,
11298,
11299,
11300,
11301,
11302,
11303,
11304,
11305,
11306,
11307,
11308,
11309,
11310,
11311,
11312,
11313,
11314,
11315,
11316,
11317,
11318,
11319,
11320,
11321,
11322,
11323,
11324,
11325,
11326,
11327,
11328,
11329,
11330,
11331,
11332,
11333,
11334,
11335,
11336,
11337,
11338,
11339,
11340,
11341,
11342,
11343,
11344,
11345,
11346,
11347,
11348,
11349,
11350,
11351,
11352,
11353,
11354,
11355,
11356,
11357,
11358,
11359,
11360,
11361,
11362,
11363,
11364,
11365,
11366,
11367,
11368,
11369,
11370,
11371,
11372,
11373,
11374,
11375,
11376,
11377,
11378,
11379,
11380,
11381,
11382,
11383,
11384,
11385,
11386,
11387,
11388,
11389,
11390,
11391,
11392,
11393,
11394,
11395,
11396,
11397,
11414,
11415,
11416,
11423,
11424,
11426,
11429
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 11429,
"ccnet_original_nlines": 429,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.27192631363868713,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.07529035210609436,
"rps_doc_frac_lines_end_with_ellipsis": 0.009302330203354359,
"rps_doc_frac_no_alph_words": 0.2803364098072052,
"rps_doc_frac_unique_words": 0.2856294512748718,
"rps_doc_mean_word_length": 5.2262468338012695,
"rps_doc_num_sentences": 171,
"rps_doc_symbol_to_word_ratio": 0.002402879996225238,
"rps_doc_unigram_entropy": 5.500576019287109,
"rps_doc_word_count": 1684,
"rps_doc_frac_chars_dupe_10grams": 0.4658561646938324,
"rps_doc_frac_chars_dupe_5grams": 0.5168730616569519,
"rps_doc_frac_chars_dupe_6grams": 0.4840359091758728,
"rps_doc_frac_chars_dupe_7grams": 0.4658561646938324,
"rps_doc_frac_chars_dupe_8grams": 0.4658561646938324,
"rps_doc_frac_chars_dupe_9grams": 0.4658561646938324,
"rps_doc_frac_chars_top_2gram": 0.020679470151662827,
"rps_doc_frac_chars_top_3gram": 0.050107941031455994,
"rps_doc_frac_chars_top_4gram": 0.06442449986934662,
"rps_doc_books_importance": -1195.430908203125,
"rps_doc_books_importance_length_correction": -1195.430908203125,
"rps_doc_openwebtext_importance": -700.7864990234375,
"rps_doc_openwebtext_importance_length_correction": -700.7864990234375,
"rps_doc_wikipedia_importance": -510.6814270019531,
"rps_doc_wikipedia_importance_length_correction": -510.6814270019531
},
"fasttext": {
"dclm": 0.04867887124419212,
"english": 0.9025639295578003,
"fineweb_edu_approx": 1.3024957180023193,
"eai_general_math": 0.17934995889663696,
"eai_open_web_math": 0.2106648087501526,
"eai_web_code": 0.03889542818069458
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.445",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.776",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "1",
"label": "Leftover HTML"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "2",
"label": "Click Here References"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "4",
"label": "Graduate/Expert Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
2,004,928,481,150,160,000
|
Desert Sky Computing
Desert Sky Computing
Remember when you first received your new computer and how much faster it felt than the one you just replaced?. No desktop clutter, you zipped around the internet and overall you were pretty happy that you bought it.
You had quick boot up from when you first turned it on to the windows opening screen. You could also keep several programs open at the same time with no problems. When did that change?
Was it just a little bit over time until one day you noticed that you were kind of sluggish again or did it happen in a day after a blue screen of death or virus infection?
It does not matter, in almost all cases we can get it back to the day we first opened the box. I say in most cases because unless we do a full format to the hard drive and reinstall, everything, which none of want to do, it will always keep some junk around. So, I am going to assume that you don't have a clone copy of your hard drive and show you some the things we can do to get it running fast enough.
Blitzkrieg Approach
Please don't let the volume of information on this page scare you. It is not hard to do, in fact much is extremely easy. I wanted to cover as many things as possible because you might have the one thing no one else has.
If this is the first time you are going to optimize your computer, we are going to assume everything is wrong, From excessive junk files to a virus we are going to hit it with a multilayered attack. Why, because we can and by checking everything you will know if you have gotten it all. This is not hard work, it can be time consuming but go watch a movie or have a cup of coffee, you don't have to be around for a lot of this. First of all, lets take a look at what slows a computer down and wow are there a lot of things.
1. 01. Unnecessary programs taking up valuable disk space
2. 02. Unnecessary files loading in your start-up
3. 03. AdWare flashing pop-ups and/or redirecting you to websites you did not plan on going to.
4. 04. A virus infection caught from an attached file in you mail or infected from a download.
5. 05. Malware like rootkits, worms, Trojans and the list goes on.
6. 06. Junk files filling up your Internet Temporary files folder or an overstuffed recycle bin.
7. 07. A badly defragmented hard drive
8. 08. A badly defragmented Windows registry
9. 09. Broken links and other issues in your registry
10. 10. Not enough room on your hard drive
11. 11. Windows settings working against you.
12. 12. Newer programs that require more memory
13. 13. Slow protection software running in the background
14. 14. Too many programs
I told you there were a lot. Most however are easily fixed. Let's break them down into types.
Items 01, 02, 06, 08, 09, 10, can be corrected with simple Optimization software.
Items 03, 04, 05 can be corrected with a group of files that can be downloaded free from the internet.
Items 07, 10, 11, can be corrected with Windows files probably already on your computer.
Finally, items 12 13 and 14 can be corrected with hardware or software changes.
Now how did we get so slow? There are a lot of reasons your computer appears slow and most of them are just poor housekeeping, Did you know that every time you view a page in a browser like Internet Explorer or Chrome or Firefox, you pick up temporary internet files that can stay on your computer until you remove them. Every time you delete a program, Windows knows you might want a second chance at getting that back so it stores the deleted file in the Recycle Bin. So deleting a fiel from you computer still leaves it on your computer on your hard drive and in the registry,
Obviously if you are infected with malicious software it will slow you down if for no other reason than it is going to do what it wants to do and not what you want to do.
Over time a 500G hard drive seems beyond an every day user but you would be surprised, Loading movies, songs and photos on your computer can use enormous amounts of space. As far as memory goes, that 1g of memory will not cut it any more and no one should be operating with less than 4g. I recommend 8g, a bit of a luxury but it will help your computer multitask a lot faster. I use 32g which is excessive but I am a bit of a nerd, you do not need anything like that.
And then there is Bloatware, a lot of bloatware comes on some computers, games, photo editing software, most of which is just a bunch of junk that creates revenue for the computer manufacturer by allowing third party vendors to put it on our computer. When you download a file from the internet you may be unintentionally downloading bloatware in the background like the large number of Toolbars available for your browser, Yahoo Toolbar, Google Toolbar, Conduit Search, Bling Toolbar, the list goes on and on. You DO NOT NEED THEM!. You may want one and that is fine it is your choice but every browser has what it need to operate without extra add-ons which are bloatware. They will slow you down.
Windows Registery
Windows uses a database to store all the configuration settings and options for operating your computer effectively. It is called the Windows Registry, Not only does Windows use it but every program you put in your computer must use it. They must register with windows and without getting into technical terms, they don't always work well together. Sometimes, when you delete a program from your computer bits and pieces leave themselves behind. Even Windows itself can loose track of where some programs are supposed to be and this confusion causes you time. Imagine if you were told to look behind door number 4 for something but someone has moved it behind door 6 now you are headstrong and every time you look you are going to check door 4 first because that is where it is supposed to be. That is what windows does in a way. It does things pretty fast but the more things it has to do does add up. So cleaning the registry is something that you should do on a regular basis. There is software that will take care of it for you but it is an unnecessary expense. We are going to use Free Software that does exactly the same thing the only difference is you have to push the buttons, are you tough enough to do that?
Junk Files
Junk files are any files that no longer serve a purpose on your computer and there may be a lot of them. Some legitmet software creates an enormous amount of junk files on your computer Google Earth is a good example. and some just accumulates over time like browsing on the internet. In any case you don't need them and they are very easy to remove. Once again you can buy some fancy software that will do it automatically but many companies make a free version of the same program that you operate manually. Other hardware manufacturers are just as bad, printers, scanners, and DVD/CD players can add programs to your computer. Even your computer adds files to temp folders that should be cleaned.
Viruses, Malware, Adware And Other Malicious Software
This category of items is a little more difficult to remove from your machine but by following my instructions it will be easy. We will check first to see if you have them and then explain how to delete them. Once again, we will be going with the free option because if you already have them, the free version will remove them just as easy as the paid version. In the long run though, I recommend buying a "Security Suite" that will protect you from getting infected in the first place. Check here to see my recommendations.
Hardware Changes
Some things just need to be upgraded! If you computer came with less than 4g memory or you hard drive was pretty small in the first place or even if the graphic card installed on your computer is too slow, With the proper instructions they are all very easy to upgrade.
Software Upgrades
You must keep you computer software updated to perform efficiently. Most windows and internet program upgrades include security fixes that also protect you from infection. You may be using what is often called "Hogware" or programs that hog all your resources just to run. Most of these can be replace with more streamlined versions or updated. Main offenders are antivirus programs, antispyware, or similar types of programs that run in the background and do so ineffectively. Antivirus programs should have a small footprint, meaning it does not take up a lot of storage space and should run while your computer is not being used and perform scans quickly. Unfortunately, some are just the opposite. they take up so many resources protecting you that they slow you down more than help.
Window Issues
Computer hard drives can get overloaded with unnecessary programs, constantly adding and deleting files can overtime defrag your hard drive and you need to reorganize it like your sock drawer only it is all done automatically for you. Drivers can become outdated and not function properly. These are all problems that windows can take care of for you. As a matter of fact Windows has a large number of programs that most users never knew existed and therefore don't use. i will be covering these on another page. They will take you to the next level of efficiency.
bloat
|
{
"url": "http://www.desertskycomp.com/optimize.html",
"source_domain": "www.desertskycomp.com",
"snapshot_id": "crawl=CC-MAIN-2019-18",
"warc_metadata": {
"Content-Length": "18743",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:R5FEESSOPKLRSYPMX64ATJIG55D55KXE",
"WARC-Concurrent-To": "<urn:uuid:2948a3d8-163c-4bbf-ad6e-5b196cdb7af7>",
"WARC-Date": "2019-04-18T11:05:37Z",
"WARC-IP-Address": "208.97.148.27",
"WARC-Identified-Payload-Type": "application/xhtml+xml",
"WARC-Payload-Digest": "sha1:LSBGLIZM3V2ORPCIWSJBECKUYXR7EHWK",
"WARC-Record-ID": "<urn:uuid:1e0eee3c-10f2-4cd5-a94c-c3f448ed6ec3>",
"WARC-Target-URI": "http://www.desertskycomp.com/optimize.html",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:07508d8e-72c5-4559-80e3-1afb08fc5044>"
},
"warc_info": "isPartOf: CC-MAIN-2019-18\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for April 2019\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-144-182-216.ec2.internal\r\nsoftware: Apache Nutch 1.15 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.1-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
23,
24,
45,
46,
265,
266,
453,
454,
629,
630,
1039,
1040,
1060,
1061,
1283,
1284,
1812,
1813,
1873,
1925,
2023,
2120,
2189,
2288,
2329,
2376,
2432,
2477,
2525,
2575,
2636,
2664,
2665,
2761,
2762,
2846,
2847,
2950,
2951,
3040,
3041,
3121,
3122,
3706,
3707,
3878,
3879,
4350,
4351,
5055,
5056,
5058,
5059,
5077,
5078,
6310,
6311,
6322,
6323,
7026,
7027,
7081,
7082,
7609,
7610,
7627,
7628,
7901,
7902,
7920,
7921,
8718,
8719,
8733,
8734,
9303,
9304,
9306,
9307
],
"line_end_idx": [
23,
24,
45,
46,
265,
266,
453,
454,
629,
630,
1039,
1040,
1060,
1061,
1283,
1284,
1812,
1813,
1873,
1925,
2023,
2120,
2189,
2288,
2329,
2376,
2432,
2477,
2525,
2575,
2636,
2664,
2665,
2761,
2762,
2846,
2847,
2950,
2951,
3040,
3041,
3121,
3122,
3706,
3707,
3878,
3879,
4350,
4351,
5055,
5056,
5058,
5059,
5077,
5078,
6310,
6311,
6322,
6323,
7026,
7027,
7081,
7082,
7609,
7610,
7627,
7628,
7901,
7902,
7920,
7921,
8718,
8719,
8733,
8734,
9303,
9304,
9306,
9307,
9313
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 9313,
"ccnet_original_nlines": 79,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.5095642805099487,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.009564289823174477,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.12433581054210663,
"rps_doc_frac_unique_words": 0.3190730810165405,
"rps_doc_mean_word_length": 4.344622611999512,
"rps_doc_num_sentences": 109,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 5.5149617195129395,
"rps_doc_word_count": 1683,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.026258209720253944,
"rps_doc_frac_chars_top_3gram": 0.013402629643678665,
"rps_doc_frac_chars_top_4gram": 0.009846829809248447,
"rps_doc_books_importance": -718.1439819335938,
"rps_doc_books_importance_length_correction": -718.1439819335938,
"rps_doc_openwebtext_importance": -316.8666687011719,
"rps_doc_openwebtext_importance_length_correction": -316.8666687011719,
"rps_doc_wikipedia_importance": -243.5328369140625,
"rps_doc_wikipedia_importance_length_correction": -243.5328369140625
},
"fasttext": {
"dclm": 0.7146254181861877,
"english": 0.9472824931144714,
"fineweb_edu_approx": 1.8205506801605225,
"eai_general_math": 0.2938994765281677,
"eai_open_web_math": 0.24852246046066284,
"eai_web_code": 0.10445964336395264
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.05",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "005.456",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "2",
"label": "Click Here References"
}
},
"document_type_v2": {
"primary": {
"code": "23",
"label": "Tutorial"
},
"secondary": {
"code": "21",
"label": "Customer Support"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "1",
"label": "General Audience"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
4,245,635,840,804,872,000
|
cancel
Showing results for
Search instead for
Did you mean:
High End Ram + FCLK Questions
thebluecoat
Level 7
Hello ROG Fam,
*I recently built a new desktop PC, to replace a 12 year old system.
Specs:
5800x
360mm AIO CPU Cooler Corsair h150i Elite Cappelix*
32GB (2x16) Corsair 3600Mhz CL18 (18-22-22-42)
X570 Asus Rog Crosshair VIII Hero (non WiFi)
1TB WD SN850 Gen4 NVME
Corsair RM1000x PSU
EVGA RTX 3080 Ti FTW3 Ultra*
Monitor:
1440p w/ 165hz Refresh Rate w/HDR *
Sort having some buyers remorse regarding the RAM, wanting to eek out
that last bit of performance so I’d be pretty much set for a long while
by having the higher end of what’s available now. Also to eek out that extra couple FPS.
I was looking at these:
*
F4-4000C14D-32GTZN
G.Skill Trident Z Neo 4000Mhz CL14 (14-15-15-35)
***
F4-3800C14D-32GTZN
G.Skill Trident Z Neo*3800Mhz CL14 (14-16-16-36)
I’d prefer the 4000mhz RAM but I’m concerned
about a few things:
How would one know if their FCLK would go that high
before purchase? Can you OC ur FCLK beforehand with
lower speed Ram first, if it posts then I’m good to go?
*
Neither is on the QVL list, anything 4000Mhz on the QVL
is like CL17-19*
I learned that XMP of 3600Mhz is already an overclock
and that the FCLK running 1:1 @1800mhz is overclocked to accommodate.
Does anybody who has this board have higher speed RAM above 3600mhz
and could get that XMP profile to post without issue ?
If I confirm I can’t post, that would mean I’d have to just seek RAM with lower timings?
*I tried Ryzen DRAM calculator to try and tighten timings and once I told it I had Micron
die or whatever it said not supported. I’d rather just buy lower latency as stock tbh.
I was able to get my FCLK to 1866Mhz and RAM to 3733Mhz
although my timings exploded to (26-26-58-88) *just to mention.
**I’d appreciate any advisement**
3,652 Views
1 REPLY 1
RedSector73
Level 12
FCLK ideally runs at half the memory speed and in sync, as a general rule. So memory running DDR@3200 will have FCLK of @1600. The FCLK is the speed of the memory controller, the Infinity Fabric and actually the RAM memory, however the RAM memory is read twice per cycle and therefore FLCK of 1600 is DDR@3200 speed.
89665
That explained, going to talk with memory speeds and assume the above rule with FCLK (is half and synced) from now on.
In the above graphic, the line in the sand sits DDR@3800 to maintain 1:1 sync ratio however Dark Hero motherboard, Ryzen 5000 series and G.Skill kit have pushed this line to DDR@4000 and few people that are good at overclocking game on other systems and there maybe other appoved systems (not kept following consider this general information about the top of the line being DDR@4000). Your system can run upwards to least DDR@4800 however it comes with using 2:1 divide and this makes for a latency penalty in the Infinity Fabric (ie: not worth running or considering). I have run my system to DDR@4800 2:1 with my old samsung b-die (not the ones currently use) and the graph suggests AMD ran to DDR@5133 ?2:1? on Ryzen 3000 series.
For gaming (for best FPS results), you will want
2xDual Rank (DR) memory kit; or
4xSingle Rank (SR) memory kit
So of the kits you have selected they are both top tier (4xSR Samsung B-die kits) and you should be able to run DDR@3800 one without issue. Since I own DDR3800 one and fair few others, if you want to save coin and see very little difference get DDR@3600 2xDR or 4xSR at lowest CL willing to pay (think that is CL14) or if money is no object consider your current selection of DDR@3800 CL14. I would not consider the DDR@4000 or higher, myself however I did find this information (graphic below) which suggest the Infinity Fabric changes in 5000 series support higher DDR@4000 speed (note the Good luck! on the slide).
89666
Hope you find this helpful.
|
{
"url": "https://rog-forum.asus.com/t5/hardware-build-advice/high-end-ram-fclk-questions/m-p/804353/highlight/true",
"source_domain": "rog-forum.asus.com",
"snapshot_id": "CC-MAIN-2024-10",
"warc_metadata": {
"Content-Length": "254297",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:UZEYWBY3OVXTIKPTQJNTRGENPADV74SM",
"WARC-Concurrent-To": "<urn:uuid:414d308d-c4cf-4d05-ac9a-356a8fca04cb>",
"WARC-Date": "2024-02-24T05:40:06Z",
"WARC-IP-Address": "18.67.65.116",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:3CQZ25E4MOULKM7EHRXZ5WMFXVAS7KJA",
"WARC-Record-ID": "<urn:uuid:220a897a-1908-4fd3-907c-c3d766789dc5>",
"WARC-Target-URI": "https://rog-forum.asus.com/t5/hardware-build-advice/high-end-ram-fclk-questions/m-p/804353/highlight/true",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:c7e449d5-5d9f-4c30-8cff-28b0a449595c>"
},
"warc_info": "isPartOf: CC-MAIN-2024-10\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for February/March 2024\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-123\r\nsoftware: Apache Nutch 1.19 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.5-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
7,
28,
48,
63,
64,
94,
95,
107,
115,
130,
131,
132,
201,
202,
209,
215,
266,
313,
358,
381,
401,
430,
431,
440,
476,
477,
547,
619,
708,
709,
733,
735,
754,
803,
807,
826,
875,
876,
921,
941,
942,
994,
1046,
1102,
1104,
1160,
1177,
1178,
1232,
1302,
1303,
1371,
1426,
1427,
1516,
1517,
1518,
1608,
1695,
1696,
1752,
1816,
1817,
1851,
1863,
1873,
1874,
1886,
1895,
2212,
2218,
2219,
2338,
2339,
3072,
3073,
3122,
3123,
3155,
3185,
3186,
3187,
3805,
3811,
3812,
3813,
3814
],
"line_end_idx": [
7,
28,
48,
63,
64,
94,
95,
107,
115,
130,
131,
132,
201,
202,
209,
215,
266,
313,
358,
381,
401,
430,
431,
440,
476,
477,
547,
619,
708,
709,
733,
735,
754,
803,
807,
826,
875,
876,
921,
941,
942,
994,
1046,
1102,
1104,
1160,
1177,
1178,
1232,
1302,
1303,
1371,
1426,
1427,
1516,
1517,
1518,
1608,
1695,
1696,
1752,
1816,
1817,
1851,
1863,
1873,
1874,
1886,
1895,
2212,
2218,
2219,
2338,
2339,
3072,
3073,
3122,
3123,
3155,
3185,
3186,
3187,
3805,
3811,
3812,
3813,
3814,
3841
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 3841,
"ccnet_original_nlines": 87,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.36000001430511475,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.1120000034570694,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.22857142984867096,
"rps_doc_frac_unique_words": 0.5309734344482422,
"rps_doc_mean_word_length": 4.401179790496826,
"rps_doc_num_sentences": 28,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 5.482528209686279,
"rps_doc_word_count": 678,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.006032169796526432,
"rps_doc_frac_chars_top_3gram": 0.01709114946424961,
"rps_doc_frac_chars_top_4gram": 0.008042899891734123,
"rps_doc_books_importance": -402.80157470703125,
"rps_doc_books_importance_length_correction": -402.80157470703125,
"rps_doc_openwebtext_importance": -230.92303466796875,
"rps_doc_openwebtext_importance_length_correction": -230.92303466796875,
"rps_doc_wikipedia_importance": -166.1862030029297,
"rps_doc_wikipedia_importance_length_correction": -166.1862030029297
},
"fasttext": {
"dclm": 0.15501290559768677,
"english": 0.9254788160324097,
"fineweb_edu_approx": 1.161699891090393,
"eai_general_math": 0.25277799367904663,
"eai_open_web_math": 0.2835032343864441,
"eai_web_code": 0.05762689933180809
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.16",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "-1",
"labels": {
"level_1": "",
"level_2": "",
"level_3": ""
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "4",
"label": "Missing Images or Figures"
},
"secondary": {
"code": "0",
"label": "No missing content"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-699,741,478,809,506,000
|
Up to 50% Off Everything! Code: LOVE18 Ends: 1/22 Details
Apply
Geometry project
Hello, you either have JavaScript turned off or an old version of Adobe's Flash Player. Get the latest Flash player.
Geometry project - Page Text Content
BC: Midsement of a triangle- is a segment whose enpoints are the midpoints of 2 sides of the triangle M=1/2(b1+b2)
FC: WHAT I LEARNED IN GEOMETRY CLASS | Christian Larios S02
1: Midpoint-the point on a line segment that is the sme distiance from both endpoints
2: Arc of a circle-part of the circle between two endpoints on the circle -major arc:named using 3 letters minor arc:named using 2 letters
3: Diameter-a line segment that has the center of the circle as one of its endpoints
4: Complementary angels-two angels whose sum is 90 degrees
5: Supplementary-two angels whose sum is 180 degrees
6: Linear pair angels-2 adjacent angels whose sum is 180 degrees
7: angel bisector-a ray whose endpoint is the vertex of an angel and that divides into congruent angels
8: Vertical Angels-two angels whose sides form opposite rays.
9: Mathematical sentence-is one in which a fact or complete idea is expressed because a mathematical sentence is a fact, many of them are judged true or false
10: Negation- this statement can usually be formed by placing the word "not," into the original statement
11: Conjunction- a compound statement formed by joining two or more simple statements with the word AND
12: Disjunctions- a compound statement formed by joining two or more simple statements with the word or
13: Point of concurrency-the point of intersection when 3 or more lines intersect.
14: Incenter- the point where 3 bisectors intersect
15: Circumcenter- the 3 perpendicular bisectors intersect on a common pont
16: Altitude-a segment from 1 vertex of a triangle to the opposite sides that the line segment is perpendicular to the side
17: SSS- all 3 sides in 1 triangle are congruent to all 3 sides in the other triangle, angels can have different measures
18: CPCTC- if the corresponding parts of two triangles are congruent then the two triangles are congruent
19: properties of parallelograms- -2 sets of parallel sides -2 sets of congruent sides -opposite angels congruent -consecutive angels supplementary -diagnals from 2 congruent triangles
Sizes: mini|medium|large|super size
Default User
• By: Christian l.
• Joined: about 5 years ago
• Published Mixbooks: 1
No contributors
About This Mixbook
• Title: Geometry project
• hope i get a good grade so i can enter the soccer team
• Tags: None
• Published: about 5 years ago
Sign up and get up to
50% off on your first order
Sign up and get up to
50% off on your first order
|
{
"url": "https://www.mixbook.com/photo-books/interests/geometry-project-8701092?vk=mK4wXkUjgU",
"source_domain": "www.mixbook.com",
"snapshot_id": "crawl=CC-MAIN-2018-05",
"warc_metadata": {
"Content-Length": "130789",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:NAO6PVOSK5BXNPWDT3AYECY55IUXBE6I",
"WARC-Concurrent-To": "<urn:uuid:00ca9179-980e-403c-b689-f7c34b00f3ee>",
"WARC-Date": "2018-01-23T04:20:50Z",
"WARC-IP-Address": "64.71.161.169",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:FNWR4Z42HL55LG2Q57HHJR3FSGBYL65X",
"WARC-Record-ID": "<urn:uuid:b5242f28-6fda-4711-9220-4d60ab73b1b6>",
"WARC-Target-URI": "https://www.mixbook.com/photo-books/interests/geometry-project-8701092?vk=mK4wXkUjgU",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:2aceab9a-0bb3-4fd7-9f17-cf009265187c>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-146-219-137.ec2.internal\r\nsoftware: Nutch 1.6 (CC)\r\nisPartOf: CC-MAIN-2018-05\r\noperator: Common Crawl Admin\r\ndescription: Wide crawl of the web for January 2018\r\npublisher: Common Crawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
58,
64,
65,
82,
83,
200,
201,
238,
239,
354,
355,
415,
416,
502,
503,
642,
643,
728,
729,
788,
789,
842,
843,
908,
909,
1013,
1014,
1076,
1077,
1236,
1237,
1343,
1344,
1448,
1449,
1553,
1554,
1637,
1638,
1690,
1691,
1766,
1767,
1891,
1892,
2014,
2015,
2121,
2122,
2307,
2308,
2344,
2357,
2378,
2408,
2434,
2450,
2451,
2470,
2471,
2499,
2558,
2573,
2606,
2607,
2629,
2657,
2658,
2680
],
"line_end_idx": [
58,
64,
65,
82,
83,
200,
201,
238,
239,
354,
355,
415,
416,
502,
503,
642,
643,
728,
729,
788,
789,
842,
843,
908,
909,
1013,
1014,
1076,
1077,
1236,
1237,
1343,
1344,
1448,
1449,
1553,
1554,
1637,
1638,
1690,
1691,
1766,
1767,
1891,
1892,
2014,
2015,
2121,
2122,
2307,
2308,
2344,
2357,
2378,
2408,
2434,
2450,
2451,
2470,
2471,
2499,
2558,
2573,
2606,
2607,
2629,
2657,
2658,
2680,
2707
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 2707,
"ccnet_original_nlines": 69,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.32854577898979187,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.025134649127721786,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.24596050381660461,
"rps_doc_frac_unique_words": 0.4878048896789551,
"rps_doc_mean_word_length": 4.716186046600342,
"rps_doc_num_sentences": 7,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 5.02152681350708,
"rps_doc_word_count": 451,
"rps_doc_frac_chars_dupe_10grams": 0.0996709018945694,
"rps_doc_frac_chars_dupe_5grams": 0.12411847710609436,
"rps_doc_frac_chars_dupe_6grams": 0.12411847710609436,
"rps_doc_frac_chars_dupe_7grams": 0.0996709018945694,
"rps_doc_frac_chars_dupe_8grams": 0.0996709018945694,
"rps_doc_frac_chars_dupe_9grams": 0.0996709018945694,
"rps_doc_frac_chars_top_2gram": 0.02068641036748886,
"rps_doc_frac_chars_top_3gram": 0.008462619967758656,
"rps_doc_frac_chars_top_4gram": 0.012693939730525017,
"rps_doc_books_importance": -235.2478790283203,
"rps_doc_books_importance_length_correction": -235.2478790283203,
"rps_doc_openwebtext_importance": -115.54092407226562,
"rps_doc_openwebtext_importance_length_correction": -115.54092407226562,
"rps_doc_wikipedia_importance": -86.49504089355469,
"rps_doc_wikipedia_importance_length_correction": -86.49504089355469
},
"fasttext": {
"dclm": 0.08241021633148193,
"english": 0.8654623031616211,
"fineweb_edu_approx": 2.2627289295196533,
"eai_general_math": 0.723292350769043,
"eai_open_web_math": 0.2105432152748108,
"eai_web_code": 0.014875889755785465
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "516",
"labels": {
"level_1": "Science and Natural history",
"level_2": "Mathematics",
"level_3": "Geometry, Algebraic"
}
},
"secondary": {
"code": "372.7",
"labels": {
"level_1": "Social sciences",
"level_2": "Education",
"level_3": "Education, Elementary and Kindergarten"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "1",
"label": "Factual"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "4",
"label": "Missing Images or Figures"
}
},
"document_type_v2": {
"primary": {
"code": "23",
"label": "Tutorial"
},
"secondary": {
"code": "10",
"label": "Knowledge Article"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "1",
"label": "No Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "2",
"label": "Partially Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "1",
"label": "General Audience"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
1,369,645,427,809,439,500
|
In Unity 5.3, how do I detect a touch on a sprite in a 2D game?
I am making a game for pre-literate kids. I need to move to the next scene automatically when they have touched all the specific sprites in a scene. Because kids will poke at everything, I need to identify the touch on the sprite and, if it has not been touched before, increment a counter. Then, when all the correct sprites in the scene have been touched, I’ll move to the next scene. But I have been unable to detect the touch on the sprite. Are there any example scripts?
I used the button approach for another scene, but it means there is still a boundary around the sprite, so that would not be as desirable for this scene.
The second choice is my preferred one, but I can’t seem to write a script that is correct that detects when the colliders are touched. An example script would be much appreciated.
The idea of disabling the script once the sprite is touched is great. Thanks.
There are several ways to do this.
You could make them buttons that call a function when touched. If the function requires an ID, and each sprite passes a unique ID to the function, you could keep track of which IDs have already been touched.
You could add colliders to the sprites and a script that detect when the colliders are touched. The script could send a signal to a central script when it’s touched and then disable itself, so further touch of that sprite would not be detected.
|
{
"url": "https://discussions.unity.com/t/in-unity-5-3-how-do-i-detect-a-touch-on-a-sprite-in-a-2d-game/166033",
"source_domain": "discussions.unity.com",
"snapshot_id": "CC-MAIN-2024-10",
"warc_metadata": {
"Content-Length": "27747",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:4SJZXNR4C3RNJN4J4O32WW6Q3NF46MYL",
"WARC-Concurrent-To": "<urn:uuid:8baf1bd5-b9b7-4a99-9a7d-38bc901a3f4e>",
"WARC-Date": "2024-03-04T11:03:09Z",
"WARC-IP-Address": "184.104.178.75",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:MIWSBHVJQAE7Y2FRGYPNIXQ3XQTLM2J3",
"WARC-Record-ID": "<urn:uuid:6a4bf9ed-d568-4e18-b1de-a5f3f3f34427>",
"WARC-Target-URI": "https://discussions.unity.com/t/in-unity-5-3-how-do-i-detect-a-touch-on-a-sprite-in-a-2d-game/166033",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:93ac1827-8ce5-4029-9c80-70d5912148f7>"
},
"warc_info": "isPartOf: CC-MAIN-2024-10\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for February/March 2024\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-208\r\nsoftware: Apache Nutch 1.19 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.5-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
64,
65,
541,
542,
696,
697,
877,
878,
956,
957,
992,
993,
1201,
1202
],
"line_end_idx": [
64,
65,
541,
542,
696,
697,
877,
878,
956,
957,
992,
993,
1201,
1202,
1446
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 1446,
"ccnet_original_nlines": 14,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.5,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.035714291036129,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.11688312143087387,
"rps_doc_frac_unique_words": 0.4498141407966614,
"rps_doc_mean_word_length": 4.237918376922607,
"rps_doc_num_sentences": 18,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.396885395050049,
"rps_doc_word_count": 269,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.11052632331848145,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.017543859779834747,
"rps_doc_frac_chars_top_3gram": 0.012280699796974659,
"rps_doc_frac_chars_top_4gram": 0.02280702069401741,
"rps_doc_books_importance": -143.68052673339844,
"rps_doc_books_importance_length_correction": -139.99009704589844,
"rps_doc_openwebtext_importance": -88.6866226196289,
"rps_doc_openwebtext_importance_length_correction": -88.6866226196289,
"rps_doc_wikipedia_importance": -77.31270599365234,
"rps_doc_wikipedia_importance_length_correction": -69.16929626464844
},
"fasttext": {
"dclm": 0.9505841135978699,
"english": 0.953812837600708,
"fineweb_edu_approx": 2.3347928524017334,
"eai_general_math": 0.9586907625198364,
"eai_open_web_math": 0.10305582731962204,
"eai_web_code": 0.969643235206604
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "794.8",
"labels": {
"level_1": "Arts",
"level_2": "Amusements and Recreation",
"level_3": ""
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-2,319,086,868,640,227,300
|
Easy-to-follow video tutorials help you learn software, creative, and business skills.Become a member
Enabling a pause feature
From: Building and Monetizing Game Apps for Android
Video: Enabling a pause feature
Now we'll look at how to pause the game, stop all the animation during the gameplay and have an option to resume or go to the main menu. So let's jump over to the Pause class and we'll start in the header file to just look at the properties and methods that exist for this class, and then go over to the Pause.cpp. In the init method we will give a value to pauseButton and we will set that equal to CCMenuItemSprite::create and then we need to pass in a sprite for the default sprite and then the secondary sprite.
Enabling a pause feature
Now we'll look at how to pause the game, stop all the animation during the gameplay and have an option to resume or go to the main menu. So let's jump over to the Pause class and we'll start in the header file to just look at the properties and methods that exist for this class, and then go over to the Pause.cpp. In the init method we will give a value to pauseButton and we will set that equal to CCMenuItemSprite::create and then we need to pass in a sprite for the default sprite and then the secondary sprite.
The default sprite is going to be a CCSprite that we will create right here, this is going to be createWithSpriteFrameName and the FrameName is pause_button.png. Second parameter for CCMenuItemSprite:: create is the selected sprite which we'll pass in NULL, then the target which is this, and the selector we want to run. And remember you have to pass in a special format for that, that's' menu_selector and in the parentheses we pass in the selector which is Pause::pause.
Make sure you don't run the method here that you just reference it. Go to the next line and we will create a CCMenu and we will call this menu, set it equal to CCMenu::create and we will pass in pauseButton and then NULL, terminate the list of objects. Then we are going to set the position of the menu, so menu->setPosition and here I am not going to adjust the Anchor point, but I am going to put the pause button in the bottom right of the screen. The reason I don't want to adjust the anchor point is because we are controlling the position of the menu and the pause button, and they have relative coordinates to each other.
I have had a lot of problems with laying out menus and their individual buttons by using anchor points, so I always leave the default anchor points in the case of buttons and menu items. So we'll pass in the ccp here and then this is going to be Utils::s().width - pauseButton->getContentSize().width/2, and the Y position is just going to be half the pauseButton's height, which we will align it with the bottom of the screen.
So pauseButton->getContentSize().height/2. Then we are going to add it as a child of the pause layer, so this->addChild and then we will pass in menu and 1. So the Z position is going to be 1 and now we are going to give the value to the pop up object. So popup = Popup::popupWithTitle. We'll pass in a string for the title which is going to be PAUSED, and on the next line we will run addButtonWithText. so popup->addButtonWithText(), now we need to pass in the text for the button which is going to be RESUME.
Target is this, selector is menu_ selector and then we pass in the method we want to run, that's going to be Pause::resume. Then on the next line we will do the same thing, so I am going to copy and paste the previous line of code and change the text to MAIN to go the Main Menu, and the method that I want to run is Pause::mainMenu. Now you may wonder why I don't just run MainMenu, mainMenu since that already exists to take us to the Main menu.
That's because we are running an instance method here. We pass in this and that grabs the target and it runs a selector on the target, which is mainMenu. I will show you how I chose to work that below here. On the next line of code, add the popup as a child. So this->addChild, pass in the popup, z of 1. Remember you can share z values, it just puts the objects you add later in front of the earlier added objects. So in Pause::pause, I am going to run this->togglePause, pass in true and then we will just copy and paste this into resume, pass in false.
In mainMenu we will run MainMenu::mainMenu. Then we'll return to the MainMenu and in togglePause we will show the popup. It's popup->show, remember we need to pass in whether or not to show or hide the pop-up, so we just pass in that pause parameter. And if we want the game to pause, then we will show the popup, if not we won't show it. So the next line, Utils::gameLayer(), then we are going to setTouchEnabled to the opposite of paused, so !paused.
So that way if we paused the game, then Touch is disabled in the gameLayer and if we unpause the game then touch is enabled again. Go to the next line, and we are going to hide the pause button based on whether the game is paused. Pause Button->setVisible and we will pass in !paused. So again if the game is paused, we want to hide the pause button, and if the game is resuming we want to show the pause button. So let's Save and test this out in the emulator. Okay, I will click the Play button and then I should be able to pause the game when I click the Pause button.
(music playing) So the music stops as specified in the popup class, I can chose to resume the game or go to the Main Menu. (music playing) I resume and the animation continues. I can pause again that I can go to the main menu and there we are. So now if you ever want to pause your game, make sure to setTouchEnabled to false in the gameLayer and then you can use this popup class or create one of your own and use the similar method to stop audio and to pause the scheduler and actions.
Show transcript
This video is part of
Image for Building and Monetizing Game Apps for Android
Building and Monetizing Game Apps for Android
55 video lessons · 10575 viewers
Todd Perkins
Author
Expand all | Collapse all
1. 5m 1s
1. Welcome
59s
2. Using the exercise files
2m 36s
3. What you should know before starting this course
25s
4. Viewing the finished game
1m 1s
2. 19m 49s
1. Understanding and downloading Cocos2d-x
2m 16s
2. Downloading the Android NDK
1m 49s
3. Creating a Cocos2d-x project template for Eclipse
4m 51s
4. Finishing the project template
1m 4s
5. Preparing Eclipse to use C++
1m 9s
6. Importing the project into Eclipse
3m 48s
7. Adding GLES 2.0 support to your emulator
3m 45s
8. Fixing additional compiler issues
1m 7s
3. 52m 7s
1. Understanding scenes, layers, and sprites
2m 16s
2. Using scenes, layers, and sprites
3m 58s
3. Positioning sprites
1m 4s
4. Adjusting basic sprite properties
5m 32s
5. Handling touches
3m 54s
6. Accessing accelerometer data
6m 7s
7. Understanding Cocos2d actions
2m 37s
8. Working with sprite sheets
4m 28s
9. Creating simple frame animations
3m 44s
10. Setting a game to display in portrait mode
54s
11. Designing for multiple screens
3m 20s
12. Running Java code from C++
5m 21s
13. Running C++ code from Java
3m 31s
14. Using buttons
3m 34s
15. Playing audio
1m 47s
4. 17m 0s
1. Viewing a flowchart of the game's core classes
1m 25s
2. Creating constants and editing the AppDelegate and Main classes
4m 8s
3. Building the GameButton class
3m 38s
4. Constructing the custom pop-up menu utility
2m 52s
5. Setting up the code in the MainMenu class
2m 10s
6. Making the Utils class
2m 47s
5. 53m 13s
1. Adding the game layers and the background
5m 41s
2. Laying out moles in the Game class
4m 45s
3. Animating the moles
5m 44s
4. Displaying moles at a specified time interval
4m 39s
5. Handling touches in the game
4m 11s
6. Displaying the player's score
4m 2s
7. Handling misses
6m 27s
8. Controlling the number of moles on the screen
2m 25s
9. Adding sound
2m 31s
10. Enabling a pause feature
5m 36s
11. Displaying the game-over screen
3m 13s
12. Saving the player's high score
3m 59s
6. 6m 53s
1. Preparing your game to support Google ads
3m 14s
2. Implementing Google ads in your game
3m 39s
7. 18m 9s
1. Handling skins in your game code
4m 55s
2. Setting up in-app purchases (IAP) for an Amazon Appstore app
3m 1s
3. Implementing Amazon IAP code
4m 11s
4. Setting up IAP for Google Play
2m 38s
5. Implementing Google Play IAP code
3m 24s
8. 2m 56s
1. Using the Cocos2d-x website
1m 13s
2. Viewing additional Android game development resources
1m 43s
9. 29s
1. Goodbye
29s
Start learning today
Get unlimited access to all courses for just $25/month.
Become a member
Sometimes @lynda teaches me how to use a program and sometimes Lynda.com changes my life forever. @JosefShutter
@lynda lynda.com is an absolute life saver when it comes to learning todays software. Definitely recommend it! #higherlearning @Michael_Caraway
@lynda The best thing online! Your database of courses is great! To the mark and very helpful. Thanks! @ru22more
Got to create something yesterday I never thought I could do. #thanks @lynda @Ngventurella
I really do love @lynda as a learning platform. Never stop learning and developing, it’s probably our greatest gift as a species! @soundslikedavid
@lynda just subscribed to lynda.com all I can say its brilliant join now trust me @ButchSamurai
@lynda is an awesome resource. The membership is priceless if you take advantage of it. @diabetic_techie
One of the best decision I made this year. Buy a 1yr subscription to @lynda @cybercaptive
guys lynda.com (@lynda) is the best. So far I’ve learned Java, principles of OO programming, and now learning about MS project @lucasmitchell
Signed back up to @lynda dot com. I’ve missed it!! Proper geeking out right now! #timetolearn #geek @JayGodbold
Share a link to this course
What are exercise files?
Exercise files are the same files the author uses in the course. Save time by downloading the author's files instead of setting up your own files, and learn by following along with the instructor.
Can I take this course without the exercise files?
Yes! If you decide you would like the exercise files later, you can upgrade to a premium account any time.
Become a member Download sample files See plans and pricing
Please wait... please wait ...
Upgrade to get access to exercise files.
Exercise files video
How to use exercise files.
Learn by watching, listening, and doing, Exercise files are the same files the author uses in the course, so you can download them and follow along Premium memberships include access to all exercise files in the library.
Exercise files
Exercise files video
How to use exercise files.
For additional information on downloading and using exercise files, watch our instructional video or read the instructions in the FAQ.
This course includes free exercise files, so you can practice while you watch the course. To access all the exercise files in our library, become a Premium Member.
Are you sure you want to mark all the videos in this course as unwatched?
This will not affect your course history, your reports, or your certificates of completion for this course.
Mark all as unwatched Cancel
Congratulations
You have completed Building and Monetizing Game Apps for Android.
Return to your organization's learning portal to continue training, or close this page.
OK
Become a member to add this course to a playlist
Join today and get unlimited access to the entire library of video courses—and create as many playlists as you like.
Get started
Already a member?
Become a member to like this course.
Join today and get unlimited access to the entire library of video courses.
Get started
Already a member?
Exercise files
Learn by watching, listening, and doing! Exercise files are the same files the author uses in the course, so you can download them and follow along. Exercise files are available with all Premium memberships. Learn more
Get started
Already a Premium member?
Exercise files video
How to use exercise files.
Ask a question
Thanks for contacting us.
You’ll hear from our Customer Service team within 24 hours.
Please enter the text shown below:
The classic layout automatically defaults to the latest Flash Player.
To choose a different player, hold the cursor over your name at the top right of any lynda.com page and choose Site preferencesfrom the dropdown menu.
Continue to classic layout Stay on new layout
Exercise files
Access exercise files from a button right under the course name.
Mark videos as unwatched
Remove icons showing you already watched videos if you want to start over.
Control your viewing experience
Make the video wide, narrow, full-screen, or pop the player out of the page into its own window.
Interactive transcripts
Click on text in the transcript to jump to that spot in the video. As the video plays, the relevant spot in the transcript will be highlighted.
Are you sure you want to delete this note?
No
Your file was successfully uploaded.
Thanks for signing up.
We’ll send you a confirmation email shortly.
Sign up and receive emails about lynda.com and our online training library:
Here’s our privacy policy with more details about how we handle your information.
Keep up with news, tips, and latest courses with emails from lynda.com.
Sign up and receive emails about lynda.com and our online training library:
Here’s our privacy policy with more details about how we handle your information.
submit Lightbox submit clicked
Terms and conditions of use
We've updated our terms and conditions (now called terms of service).Go
Review and accept our updated terms of service.
|
{
"url": "http://www.lynda.com/Android-tutorials/Enabling-pause-feature/107169/126960-4.html",
"source_domain": "www.lynda.com",
"snapshot_id": "crawl=CC-MAIN-2014-41",
"warc_metadata": {
"Content-Length": "195301",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:VEGPXVRGN5A46Q634GL3UGWNUR7YPTZZ",
"WARC-Concurrent-To": "<urn:uuid:a80bb095-f33f-42ac-b443-bb5b20fc194d>",
"WARC-Date": "2014-09-16T04:15:40Z",
"WARC-IP-Address": "69.20.127.243",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:G6XMN7FM6OPZA2YAYCWCHZX6KJASDEQE",
"WARC-Record-ID": "<urn:uuid:fd594aeb-5a15-48db-b70b-c66067e8d975>",
"WARC-Target-URI": "http://www.lynda.com/Android-tutorials/Enabling-pause-feature/107169/126960-4.html",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:6dea0a34-dd17-4443-9553-02628051d729>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-196-40-205.us-west-1.compute.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2014-41\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web with URLs provided by Blekko for September 2014\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
102,
103,
128,
129,
181,
182,
214,
215,
731,
732,
757,
758,
1274,
1275,
1749,
1750,
2379,
2380,
2808,
2809,
3321,
3322,
3770,
3771,
4327,
4328,
4781,
4782,
5354,
5355,
5843,
5844,
5860,
5861,
5883,
5884,
5940,
5986,
5987,
6020,
6021,
6034,
6041,
6042,
6044,
6070,
6081,
6096,
6106,
6138,
6151,
6207,
6217,
6250,
6262,
6275,
6322,
6335,
6370,
6383,
6440,
6453,
6491,
6503,
6539,
6551,
6593,
6606,
6654,
6667,
6708,
6720,
6732,
6781,
6794,
6835,
6848,
6875,
6887,
6928,
6941,
6965,
6978,
7014,
7026,
7063,
7076,
7110,
7123,
7163,
7176,
7227,
7237,
7276,
7289,
7324,
7337,
7372,
7385,
7407,
7420,
7442,
7455,
7467,
7521,
7534,
7605,
7617,
7654,
7667,
7718,
7731,
7780,
7793,
7823,
7836,
7849,
7898,
7911,
7953,
7966,
7993,
8006,
8059,
8072,
8108,
8121,
8158,
8170,
8193,
8206,
8259,
8272,
8292,
8305,
8338,
8351,
8391,
8404,
8443,
8456,
8468,
8517,
8530,
8574,
8587,
8599,
8639,
8652,
8720,
8732,
8768,
8781,
8819,
8832,
8873,
8886,
8898,
8933,
8946,
9007,
9020,
9029,
9044,
9054,
9055,
9076,
9077,
9133,
9134,
9150,
9262,
9406,
9519,
9610,
9757,
9853,
9958,
10048,
10190,
10302,
10330,
10331,
10356,
10357,
10554,
10555,
10606,
10607,
10714,
10715,
10775,
10776,
10807,
10848,
10849,
10870,
10871,
10898,
10899,
11120,
11121,
11122,
11137,
11138,
11159,
11160,
11187,
11188,
11323,
11324,
11488,
11489,
11563,
11564,
11672,
11673,
11674,
11703,
11704,
11720,
11721,
11787,
11788,
11876,
11877,
11878,
11881,
11930,
11931,
12048,
12049,
12061,
12062,
12080,
12081,
12118,
12119,
12195,
12196,
12208,
12209,
12227,
12228,
12243,
12244,
12463,
12464,
12476,
12477,
12503,
12504,
12525,
12526,
12553,
12554,
12569,
12570,
12596,
12656,
12657,
12692,
12693,
12763,
12764,
12915,
12916,
12962,
12977,
12978,
13043,
13044,
13069,
13070,
13145,
13146,
13178,
13179,
13276,
13277,
13301,
13302,
13446,
13447,
13490,
13491,
13494,
13495,
13532,
13533,
13556,
13557,
13602,
13603,
13604,
13680,
13681,
13763,
13764,
13836,
13837,
13913,
13914,
13996,
13997,
14001,
14032,
14060,
14061,
14133
],
"line_end_idx": [
102,
103,
128,
129,
181,
182,
214,
215,
731,
732,
757,
758,
1274,
1275,
1749,
1750,
2379,
2380,
2808,
2809,
3321,
3322,
3770,
3771,
4327,
4328,
4781,
4782,
5354,
5355,
5843,
5844,
5860,
5861,
5883,
5884,
5940,
5986,
5987,
6020,
6021,
6034,
6041,
6042,
6044,
6070,
6081,
6096,
6106,
6138,
6151,
6207,
6217,
6250,
6262,
6275,
6322,
6335,
6370,
6383,
6440,
6453,
6491,
6503,
6539,
6551,
6593,
6606,
6654,
6667,
6708,
6720,
6732,
6781,
6794,
6835,
6848,
6875,
6887,
6928,
6941,
6965,
6978,
7014,
7026,
7063,
7076,
7110,
7123,
7163,
7176,
7227,
7237,
7276,
7289,
7324,
7337,
7372,
7385,
7407,
7420,
7442,
7455,
7467,
7521,
7534,
7605,
7617,
7654,
7667,
7718,
7731,
7780,
7793,
7823,
7836,
7849,
7898,
7911,
7953,
7966,
7993,
8006,
8059,
8072,
8108,
8121,
8158,
8170,
8193,
8206,
8259,
8272,
8292,
8305,
8338,
8351,
8391,
8404,
8443,
8456,
8468,
8517,
8530,
8574,
8587,
8599,
8639,
8652,
8720,
8732,
8768,
8781,
8819,
8832,
8873,
8886,
8898,
8933,
8946,
9007,
9020,
9029,
9044,
9054,
9055,
9076,
9077,
9133,
9134,
9150,
9262,
9406,
9519,
9610,
9757,
9853,
9958,
10048,
10190,
10302,
10330,
10331,
10356,
10357,
10554,
10555,
10606,
10607,
10714,
10715,
10775,
10776,
10807,
10848,
10849,
10870,
10871,
10898,
10899,
11120,
11121,
11122,
11137,
11138,
11159,
11160,
11187,
11188,
11323,
11324,
11488,
11489,
11563,
11564,
11672,
11673,
11674,
11703,
11704,
11720,
11721,
11787,
11788,
11876,
11877,
11878,
11881,
11930,
11931,
12048,
12049,
12061,
12062,
12080,
12081,
12118,
12119,
12195,
12196,
12208,
12209,
12227,
12228,
12243,
12244,
12463,
12464,
12476,
12477,
12503,
12504,
12525,
12526,
12553,
12554,
12569,
12570,
12596,
12656,
12657,
12692,
12693,
12763,
12764,
12915,
12916,
12962,
12977,
12978,
13043,
13044,
13069,
13070,
13145,
13146,
13178,
13179,
13276,
13277,
13301,
13302,
13446,
13447,
13490,
13491,
13494,
13495,
13532,
13533,
13556,
13557,
13602,
13603,
13604,
13680,
13681,
13763,
13764,
13836,
13837,
13913,
13914,
13996,
13997,
14001,
14032,
14060,
14061,
14133,
14180
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 14180,
"ccnet_original_nlines": 310,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.39757364988327026,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.01594454050064087,
"rps_doc_frac_lines_end_with_ellipsis": 0.0032154300715774298,
"rps_doc_frac_no_alph_words": 0.1590987890958786,
"rps_doc_frac_unique_words": 0.28287839889526367,
"rps_doc_mean_word_length": 4.415632724761963,
"rps_doc_num_sentences": 193,
"rps_doc_symbol_to_word_ratio": 0.0020797199103981256,
"rps_doc_unigram_entropy": 5.5942206382751465,
"rps_doc_word_count": 2418,
"rps_doc_frac_chars_dupe_10grams": 0.15238362550735474,
"rps_doc_frac_chars_dupe_5grams": 0.22309638559818268,
"rps_doc_frac_chars_dupe_6grams": 0.18310387432575226,
"rps_doc_frac_chars_dupe_7grams": 0.17439356446266174,
"rps_doc_frac_chars_dupe_8grams": 0.1560363471508026,
"rps_doc_frac_chars_dupe_9grams": 0.15238362550735474,
"rps_doc_frac_chars_top_2gram": 0.012644000351428986,
"rps_doc_frac_chars_top_3gram": 0.006743470206856728,
"rps_doc_frac_chars_top_4gram": 0.006181510165333748,
"rps_doc_books_importance": -1398.4517822265625,
"rps_doc_books_importance_length_correction": -1398.4517822265625,
"rps_doc_openwebtext_importance": -835.587158203125,
"rps_doc_openwebtext_importance_length_correction": -835.587158203125,
"rps_doc_wikipedia_importance": -671.559326171875,
"rps_doc_wikipedia_importance_length_correction": -671.559326171875
},
"fasttext": {
"dclm": 0.028763119131326675,
"english": 0.8909595608711243,
"fineweb_edu_approx": 1.3899619579315186,
"eai_general_math": 0.06546170264482498,
"eai_open_web_math": 0.06483309715986252,
"eai_web_code": 0.054230570793151855
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "794.8",
"labels": {
"level_1": "Arts",
"level_2": "Amusements and Recreation",
"level_3": ""
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "4",
"label": "Missing Images or Figures"
},
"secondary": {
"code": "0",
"label": "No missing content"
}
},
"document_type_v2": {
"primary": {
"code": "23",
"label": "Tutorial"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
7,508,675,450,632,871,000
|
Tniasm compatible assembler
صفحة 1/3
| 2 | 3
بواسطة Daemos
Paragon (1981)
صورة Daemos
13-10-2018, 21:55
Context of the story is somewhat difficult so please keep the "why do you want to do it" out of the discussion. I am using tniasm because thats what i always use. Its a good assembler, in fact somewhere in the one of the best region imho. However there is a small problem: it is a x86 binary and thats it. It works it does the job but no source no ports nothing. I will not contact the maker because i dont want to bother him with requests of this kind so i am looking for a assembler that complies to the following.
1. Can assemble complicated sources (trust me, this one is difficult)
2. Is open source.
Almost 90% of my computers at home and work are based on arm cpus so i need a assembler that can run on such platform.
To prevent the obvious awnsers:
Yes, i have tried quemu. Too slow assembly takes 15 minutes.
I have tried glass and sjasm and both trow about 1500 errors in my face.
All other suggestions are welcome. I will try anything you suggest.
Login أوregister لوضع تعليقاتك
بواسطة Manuel
Ascended (18860)
صورة Manuel
13-10-2018, 22:11
Perhaps these errors can be solved with some simple search and replace...? Probably most have the same origin...
بواسطة syn
Prophet (2097)
صورة syn
13-10-2018, 22:48
Are you talking about the old ancient tniasm v0.45 which is free to download or the paid v1.0? Not that it matters much compatibility-wise I guess but 1.0 also offers macros and stuff.
Wouldn't virtual machine or remote desktopping your main dev pc be an option?
بواسطة Daemos
Paragon (1981)
صورة Daemos
13-10-2018, 22:56
its about the acient 0.45 version. Have tried remote desktopping but its all inconvenient. On my main machine the exe runs smoothly on wine so no problems there. Its where the ARM cpu kicks in where things get difficult.
بواسطة sd_snatcher
Prophet (3511)
صورة sd_snatcher
14-10-2018, 02:39
Maybe sjasm-plus? It's more flexible than sjasm, so it might work.
بواسطة Daemos
Paragon (1981)
صورة Daemos
17-09-2020, 21:57
Sjasmplus at least compiles nicely. However compiling my sources gives 20k + errors propably label related oO
بواسطة Manuel
Ascended (18860)
صورة Manuel
14-10-2018, 17:23
Look at the errors and see how you can solve them... Maybe glass is the best option, grauw is quite active.
بواسطة Vampier
Prophet (2397)
صورة Vampier
14-10-2018, 20:58
TNIAsm1.0 is not an option?
بواسطة Daemos
Paragon (1981)
صورة Daemos
16-10-2018, 21:24
After many many manyyyyyy hours of fiddling here is what I came up with:
compile new kernel with binfmt_module. install qemu-i386 with static support. Then create i386 chroot. Transfer libs and wine binaries to main system. ENable binmft
Copy wine prefix to home folder. Start wine cmd and voila! tniasm starts and compiles on arm64. In a whopping 25 seconds hahahaha. Still kinda slow but good enough for me. Takes 53 seconds at my work on a native machine so this is a pretty good result. Thanks for thinking along.
Perhaps one day the makers of this great tool will compile a arm binary who knows for now I can continue on my portable platforms.
بواسطة Ped7g
Resident (57)
صورة Ped7g
17-09-2020, 21:57
Daemos wrote:
Sjasmplus at least compiles nicely. However compiling my sources gives 20k + errors propably label related oO
While the syntax of sjasmplus is quite versatile (to my taste actually too much), certainly it can't assemble *any* syntax and the sources may require some adjusting.
But if you can provide me with some small asm example, to see what kind of errors you have with latest sjasmplus (v1.14.2 is now out), I can help you to asses what is just simple syntax sugar solvable by some search/replace or sed, and what is serious blocking issue (and maybe you have even run into regular sjasmplus bug, then it would be welcome contribution to make me aware of it, so I can fix it in next release).
(I understand this is all time consuming process, but no report = no chance for fix, even if I would find eventually some time to look into it)
(edit: I'm not sure if the sources are available somewhere (I think not), so I can't try myself, if they are public, enlighten me with some url and I will take a look)
بواسطة Grauw
Ascended (10604)
صورة Grauw
01-11-2019, 14:55
There is no Tniasm compatible assembler except Tniasm, nor is there a Glass compatible assembler except for Glass or a Sjasm compatible assembler except for Sjasm. Same for Gen80, M80, Compass, etc. Each extend the basic assembly syntax with their own unique feature set to provide convenience to the developer at the cost of source portability.
There is no way to create an assembler which one-on-one supports the syntax and features of all other assemblers without turning into a big inconsistent do-everything mess. Also it would generate even more confusion as to what is “the interoperable syntax”, people would e.g. mix Tniasm and Sjasm syntax and as a result you would still have source code that can only be assembled by this particular one.
So the reality is that whenever you move to a different assembler, unless you use only plain interoperable assembly and none of the assembler’s more advanced features, there is some effort involved in porting the source code across. Simply because there is no standard syntax for things like scoped labels, macros, structures, or even expressions.
It can be a bit laborious however by investing some time in getting to understand the assembler feature set and some search / replacing (possibly involving regular expressions) you should get a long way in a couple of hours.
صفحة 1/3
| 2 | 3
|
{
"url": "https://msx.org/ar/node/55815?page=0",
"source_domain": "msx.org",
"snapshot_id": "crawl=CC-MAIN-2022-33",
"warc_metadata": {
"Content-Length": "23989",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:73B6GRGTI4RRPRI5BU2AIO3I7FHBQKXD",
"WARC-Concurrent-To": "<urn:uuid:18898ac1-44a2-43bd-9313-d5536f5a7722>",
"WARC-Date": "2022-08-13T09:02:25Z",
"WARC-IP-Address": "159.69.251.84",
"WARC-Identified-Payload-Type": "application/xhtml+xml",
"WARC-Payload-Digest": "sha1:SZRIHMK2SQCHWMJPEF5GSYDAYFGJ5VYA",
"WARC-Record-ID": "<urn:uuid:7dc6ed10-b22d-43da-841b-0cbc8768d12b>",
"WARC-Target-URI": "https://msx.org/ar/node/55815?page=0",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:86b7197e-7fd0-4a94-a82c-442cd3524d5e>"
},
"warc_info": "isPartOf: CC-MAIN-2022-33\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for August 2022\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-112\r\nsoftware: Apache Nutch 1.18 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.4-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
28,
29,
38,
46,
47,
61,
62,
77,
78,
90,
91,
109,
110,
627,
628,
698,
717,
718,
837,
838,
870,
871,
932,
1005,
1006,
1074,
1075,
1106,
1107,
1121,
1122,
1139,
1140,
1152,
1153,
1171,
1172,
1285,
1286,
1297,
1298,
1313,
1314,
1323,
1324,
1342,
1343,
1528,
1529,
1607,
1608,
1622,
1623,
1638,
1639,
1651,
1652,
1670,
1671,
1892,
1893,
1912,
1913,
1928,
1929,
1946,
1947,
1965,
1966,
2033,
2034,
2048,
2049,
2064,
2065,
2077,
2078,
2096,
2097,
2207,
2208,
2222,
2223,
2240,
2241,
2253,
2254,
2272,
2273,
2381,
2382,
2397,
2398,
2413,
2414,
2427,
2428,
2446,
2447,
2475,
2476,
2490,
2491,
2506,
2507,
2519,
2520,
2538,
2539,
2612,
2613,
2778,
2779,
3059,
3060,
3191,
3192,
3205,
3206,
3220,
3221,
3232,
3233,
3251,
3252,
3266,
3267,
3377,
3378,
3545,
3546,
3966,
3967,
4111,
4112,
4280,
4281,
4294,
4295,
4312,
4313,
4324,
4325,
4343,
4344,
4690,
4691,
5095,
5096,
5444,
5445,
5670,
5671,
5680
],
"line_end_idx": [
28,
29,
38,
46,
47,
61,
62,
77,
78,
90,
91,
109,
110,
627,
628,
698,
717,
718,
837,
838,
870,
871,
932,
1005,
1006,
1074,
1075,
1106,
1107,
1121,
1122,
1139,
1140,
1152,
1153,
1171,
1172,
1285,
1286,
1297,
1298,
1313,
1314,
1323,
1324,
1342,
1343,
1528,
1529,
1607,
1608,
1622,
1623,
1638,
1639,
1651,
1652,
1670,
1671,
1892,
1893,
1912,
1913,
1928,
1929,
1946,
1947,
1965,
1966,
2033,
2034,
2048,
2049,
2064,
2065,
2077,
2078,
2096,
2097,
2207,
2208,
2222,
2223,
2240,
2241,
2253,
2254,
2272,
2273,
2381,
2382,
2397,
2398,
2413,
2414,
2427,
2428,
2446,
2447,
2475,
2476,
2490,
2491,
2506,
2507,
2519,
2520,
2538,
2539,
2612,
2613,
2778,
2779,
3059,
3060,
3191,
3192,
3205,
3206,
3220,
3221,
3232,
3233,
3251,
3252,
3266,
3267,
3377,
3378,
3545,
3546,
3966,
3967,
4111,
4112,
4280,
4281,
4294,
4295,
4312,
4313,
4324,
4325,
4343,
4344,
4690,
4691,
5095,
5096,
5444,
5445,
5670,
5671,
5680,
5687
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 5687,
"ccnet_original_nlines": 154,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3845521807670593,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.01396877970546484,
"rps_doc_frac_lines_end_with_ellipsis": 0.006451610010117292,
"rps_doc_frac_no_alph_words": 0.2596548795700073,
"rps_doc_frac_unique_words": 0.4516128897666931,
"rps_doc_mean_word_length": 4.612903118133545,
"rps_doc_num_sentences": 63,
"rps_doc_symbol_to_word_ratio": 0.002465080004185438,
"rps_doc_unigram_entropy": 5.595855712890625,
"rps_doc_word_count": 961,
"rps_doc_frac_chars_dupe_10grams": 0.041055720299482346,
"rps_doc_frac_chars_dupe_5grams": 0.09384164214134216,
"rps_doc_frac_chars_dupe_6grams": 0.09384164214134216,
"rps_doc_frac_chars_dupe_7grams": 0.07060681283473969,
"rps_doc_frac_chars_dupe_8grams": 0.0595533512532711,
"rps_doc_frac_chars_dupe_9grams": 0.041055720299482346,
"rps_doc_frac_chars_top_2gram": 0.007895329967141151,
"rps_doc_frac_chars_top_3gram": 0.01714414916932583,
"rps_doc_frac_chars_top_4gram": 0.020753439515829086,
"rps_doc_books_importance": -627.9885864257812,
"rps_doc_books_importance_length_correction": -627.9885864257812,
"rps_doc_openwebtext_importance": -351.44195556640625,
"rps_doc_openwebtext_importance_length_correction": -351.44195556640625,
"rps_doc_wikipedia_importance": -234.79759216308594,
"rps_doc_wikipedia_importance_length_correction": -234.79759216308594
},
"fasttext": {
"dclm": 0.09809309244155884,
"english": 0.8732447624206543,
"fineweb_edu_approx": 1.1871750354766846,
"eai_general_math": 0.675381064414978,
"eai_open_web_math": 0.44925516843795776,
"eai_web_code": 0.43982136249542236
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.4",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.162",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "4",
"label": "Analyze"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "4",
"label": "Graduate/Expert Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-4,692,465,058,822,604,000
|
Stack Overflow is a community of 4.7 million programmers, just like you, helping each other.
Join them; it only takes a minute:
Sign up
Join the Stack Overflow community to:
1. Ask programming questions
2. Answer and help your peers
3. Get recognized for your expertise
I've been hacking classes in python like this :
def hack(f,aClass) :
class MyClass(aClass) :
def f(self) :
f()
return MyClass
A = hack(afunc,A)
Which looks pretty clean to me. It takes a class A, creates a new class derived from it, that has an extra method, calling f, and then reassigns the new clas to A.
How does this differ from metaclass hacking in Python. What are the advantages of using metaclass over this?
share|improve this question
What is the reason for doing this? – S.Lott Mar 6 '09 at 14:22
The definition of a class in python is an instance of type (or an instance of a subclass of type). In other words, the class definition itself is an object. With metaclasses, you have the ability to control the type instance that becomes the class definition.
When a metaclass is invoked, you have the ability to completely re-write the class definition. You have access to all the proposed attributes of the class, its ancestors, etc. More than just injecting a method or removing a method, you can radically alter the inheritance tree, the type, and pretty much any other aspect. You can also chain metaclasses together for a very dynamic and totally convoluted experience.
I suppose the real benefit, though is that the class's type remains the class's type. In your example, typing:
a_inst = A()
type(a_inst)
will show that it is an instance of MyClass. Yes, isinstance(a_inst, aClass) would return True, but you've introduced a subclass, rather than a dynamically re-defined class. The distinction there is probably the key.
As rjh points out, the anonymous inner class also has performance and extensibility implications. A metaclass is processed only once, and the moment that the class is defined, and never again. Users of your API can also extend your metaclass because it is not enclosed within a function, so you gain a certain degree of extensibility.
This slightly old article actually has a good explanation that compares exactly the "function decoration" approach you used in the example with metaclasses, and shows the history of the Python metaclass evolution in that context: http://www.ibm.com/developerworks/linux/library/l-pymeta.html
share|improve this answer
A metaclass is the class of a class. IMO, the bloke here covered it quite serviceably, including some use-cases:
http://stackoverflow.com/questions/395982/metaclass-new-cls-and-super-can-someone-explain-the-mechanism-exactly/396109#396109
share|improve this answer
You can use the type callable as well.
def hack(f, aClass):
newfunc = lambda self: f()
return type('MyClass', (aClass,), {'f': newfunc})
I find using type the easiest way to get into the metaclass world.
share|improve this answer
Your Answer
discard
By posting your answer, you agree to the privacy policy and terms of service.
Not the answer you're looking for? Browse other questions tagged or ask your own question.
|
{
"url": "http://stackoverflow.com/questions/618960/python-metaclasses",
"source_domain": "stackoverflow.com",
"snapshot_id": "crawl=CC-MAIN-2016-07",
"warc_metadata": {
"Content-Length": "81319",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:RSJ2VBGKFQJ2YNQDKZXQCEWNGUDBN2YG",
"WARC-Concurrent-To": "<urn:uuid:14713156-954a-4d86-aaca-cc4044e33923>",
"WARC-Date": "2016-02-10T14:29:38Z",
"WARC-IP-Address": "104.16.37.249",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:HE7UWVULFCVEDKVRAPFO3GSZFK6SHL4X",
"WARC-Record-ID": "<urn:uuid:47714c43-4596-4637-b0d0-a30fe5688f63>",
"WARC-Target-URI": "http://stackoverflow.com/questions/618960/python-metaclasses",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:0413c6bb-75de-47fa-a0e9-fb3041c0d6bd>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-236-182-209.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2016-07\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web for February 2016\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
93,
94,
129,
130,
138,
176,
207,
239,
278,
279,
327,
328,
349,
375,
394,
405,
422,
423,
441,
442,
606,
607,
716,
717,
745,
750,
813,
814,
1074,
1075,
1491,
1492,
1603,
1604,
1617,
1630,
1631,
1848,
1849,
2184,
2185,
2477,
2478,
2504,
2505,
2618,
2619,
2745,
2746,
2772,
2773,
2812,
2813,
2834,
2865,
2919,
2920,
2987,
2988,
3014,
3015,
3027,
3028,
3030,
3038,
3039,
3117,
3118
],
"line_end_idx": [
93,
94,
129,
130,
138,
176,
207,
239,
278,
279,
327,
328,
349,
375,
394,
405,
422,
423,
441,
442,
606,
607,
716,
717,
745,
750,
813,
814,
1074,
1075,
1491,
1492,
1603,
1604,
1617,
1630,
1631,
1848,
1849,
2184,
2185,
2477,
2478,
2504,
2505,
2618,
2619,
2745,
2746,
2772,
2773,
2812,
2813,
2834,
2865,
2919,
2920,
2987,
2988,
3014,
3015,
3027,
3028,
3030,
3038,
3039,
3117,
3118,
3208
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 3208,
"ccnet_original_nlines": 68,
"rps_doc_curly_bracket": 0.0006234400207176805,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.37536656856536865,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.019061580300331116,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.22873899340629578,
"rps_doc_frac_unique_words": 0.5040983557701111,
"rps_doc_mean_word_length": 5.098360538482666,
"rps_doc_num_sentences": 35,
"rps_doc_symbol_to_word_ratio": 0.001466279965825379,
"rps_doc_unigram_entropy": 4.9809184074401855,
"rps_doc_word_count": 488,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.015273310244083405,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.019292600452899933,
"rps_doc_frac_chars_top_3gram": 0.01446945033967495,
"rps_doc_frac_chars_top_4gram": 0.011254020035266876,
"rps_doc_books_importance": -253.1419219970703,
"rps_doc_books_importance_length_correction": -253.1419219970703,
"rps_doc_openwebtext_importance": -187.62425231933594,
"rps_doc_openwebtext_importance_length_correction": -187.62425231933594,
"rps_doc_wikipedia_importance": -122.46073150634766,
"rps_doc_wikipedia_importance_length_correction": -122.46073150634766
},
"fasttext": {
"dclm": 0.6679204106330872,
"english": 0.9103924036026001,
"fineweb_edu_approx": 2.374419927597046,
"eai_general_math": 0.02014004997909069,
"eai_open_web_math": 0.20098352432250977,
"eai_web_code": 0.0010186400031670928
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1332",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.133",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "0",
"label": "No missing content"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
2,049,211,054,267,712,300
|
autocomplete django template context variables
is there a way to autocomplete the variables passed into the template by the view in django?
For example, I'm passing a model into template 1 and I'd like to have pycharm show me the handy dropdown with all the model attributes when i type {{ mymodel.
the project structure looks like this
project
- apps
- app1
- templates
index.html
about.html
+ migrations
__init__.py
views.py
models.py
manage.py
6 comments
Comment actions Permalink
Could you please show how you pass the model to the template?
0
Comment actions Permalink
class StudentReportCardView(View):
template_name = "inquest/assessment/student_report_card.html"
def get(self, request, student_id):
ctx = dict()
student_profile = get_object_or_404(users_models.StudentProfile, uuid=student_id)
taken_assessments = models.StudentAssessments.objects.filter(student=student_profile.user, score__gte=0.0)
assessments_needing_graded = models.StudentAssessments.objects.filter(student=student_profile.user, score__lt=0.0)
ctx['student_profile'] = student_profile
ctx['taken_assessments'] = taken_assessments
ctx['assessments_needing_graded'] = assessments_needing_graded
return render_to_response(self.template_name, RequestContext(request, ctx))
0
Comment actions Permalink
In this case, PyCharm does not correctly identify that the template is referenced from the code because you're passing a variable, rather than a string literal, as the first argument to render_to_response. We may be able to improve PyCharm's code analysis to handle your situation too; you're welcome to file an issue at http://youtrack.jetbrains.com/
0
Comment actions Permalink
So this is the preferred way in order for PyCharm to recognize the variables?
class StudentReportCardView(View):
template_name = "inquest/assessment/student_report_card.html"
def get(self, request, student_id):
student_profile = get_object_or_404(users_models.StudentProfile, uuid=student_id)
taken_assessments = models.StudentAssessments.objects.filter(student=student_profile.user, score__gte=0.0)
assessments_needing_graded = models.StudentAssessments.objects.filter(student=student_profile.user, score__lt=0.0)
return render_to_response(self.template_name, RequestContext(request, {
'student_profile': student_profile,
'taken_assessments': taken_assessments,
'assessments_needing_graded': assessments_needing_graded,
}))
0
Comment actions Permalink
In the current version of PyCharm, in order for it to recognize the variables, you need to change the code to:
render_to_response("inquest/assessment/student_report_card.html", ...)
0
Comment actions Permalink
Ahhhh.
I read that too early in the morning to realize it said "template". I will open a ticket as Django's class based views make use of the template_name variable
https://docs.djangoproject.com/en/dev/topics/class-based-views/
0
Please sign in to leave a comment.
|
{
"url": "https://intellij-support.jetbrains.com/hc/en-us/community/posts/205809439-autocomplete-django-template-context-variables",
"source_domain": "intellij-support.jetbrains.com",
"snapshot_id": "crawl=CC-MAIN-2020-34",
"warc_metadata": {
"Content-Length": "46644",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:ZN5NH4DXY36FOV5EWPCBUK65H3FYSWH7",
"WARC-Concurrent-To": "<urn:uuid:59737d9d-384f-4daa-ba6d-3b915629abdf>",
"WARC-Date": "2020-08-14T03:17:21Z",
"WARC-IP-Address": "104.16.53.111",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:43KPUXGPR2ZB6KLFHWEGZKKEXPUXUQ2I",
"WARC-Record-ID": "<urn:uuid:b842d034-f902-40e4-bb33-728562e9c250>",
"WARC-Target-URI": "https://intellij-support.jetbrains.com/hc/en-us/community/posts/205809439-autocomplete-django-template-context-variables",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:25b68c87-9103-4de9-97be-de6ec3e2e646>"
},
"warc_info": "isPartOf: CC-MAIN-2020-34\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for August 2020\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-25.ec2.internal\r\nsoftware: Apache Nutch 1.17 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.2-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
47,
48,
141,
142,
301,
302,
340,
348,
356,
366,
383,
401,
419,
437,
454,
468,
483,
494,
505,
531,
593,
595,
621,
656,
722,
723,
763,
784,
874,
989,
1112,
1113,
1162,
1215,
1286,
1287,
1371,
1373,
1399,
1751,
1753,
1779,
1857,
1858,
1893,
1959,
1960,
2000,
2090,
2205,
2328,
2329,
2409,
2457,
2509,
2579,
2591,
2593,
2619,
2730,
2801,
2803,
2829,
2836,
2837,
2996,
2997,
3061,
3063,
3064
],
"line_end_idx": [
47,
48,
141,
142,
301,
302,
340,
348,
356,
366,
383,
401,
419,
437,
454,
468,
483,
494,
505,
531,
593,
595,
621,
656,
722,
723,
763,
784,
874,
989,
1112,
1113,
1162,
1215,
1286,
1287,
1371,
1373,
1399,
1751,
1753,
1779,
1857,
1858,
1893,
1959,
1960,
2000,
2090,
2205,
2328,
2329,
2409,
2457,
2509,
2579,
2591,
2593,
2619,
2730,
2801,
2803,
2829,
2836,
2837,
2996,
2997,
3061,
3063,
3064,
3098
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 3098,
"ccnet_original_nlines": 70,
"rps_doc_curly_bracket": 0.0012911600060760975,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.21626617014408112,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.007393720094114542,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.3382624685764313,
"rps_doc_frac_unique_words": 0.5259515643119812,
"rps_doc_mean_word_length": 7.99653959274292,
"rps_doc_num_sentences": 46,
"rps_doc_symbol_to_word_ratio": 0.0018484300235286355,
"rps_doc_unigram_entropy": 4.693528175354004,
"rps_doc_word_count": 289,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.3297273814678192,
"rps_doc_frac_chars_dupe_6grams": 0.307226300239563,
"rps_doc_frac_chars_dupe_7grams": 0.307226300239563,
"rps_doc_frac_chars_dupe_8grams": 0.307226300239563,
"rps_doc_frac_chars_dupe_9grams": 0.2154911309480667,
"rps_doc_frac_chars_top_2gram": 0.036347899585962296,
"rps_doc_frac_chars_top_3gram": 0.059714410454034805,
"rps_doc_frac_chars_top_4gram": 0.05192556977272034,
"rps_doc_books_importance": -271.2722473144531,
"rps_doc_books_importance_length_correction": -271.2722473144531,
"rps_doc_openwebtext_importance": -98.26651763916016,
"rps_doc_openwebtext_importance_length_correction": -98.26651763916016,
"rps_doc_wikipedia_importance": -63.134979248046875,
"rps_doc_wikipedia_importance_length_correction": -63.134979248046875
},
"fasttext": {
"dclm": 0.21529334783554077,
"english": 0.6510982513427734,
"fineweb_edu_approx": 2.412353992462158,
"eai_general_math": 0.09180957078933716,
"eai_open_web_math": 0.059007469564676285,
"eai_web_code": 0.03626174107193947
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.133",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.436",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "4",
"label": "Graduate/Expert Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-2,039,462,307,209,288,000
|
add share buttonsSoftshare button powered by web designing, website development company in India & developed by Bijo John : freelance website development, web designer
Online Safety Tips – How To Protect Your Passwords
Experience daily indicates that online security tips on safeguarding your passwords are essential even when safety measures, generally speaking, are extremely simple to establish. You can find the best team password manager at https://www.logmeonce.com/team-password-manager-top-features/ for the online protection of your documents.
Just wondering if this could be you.
Not, however, rather than utilizing online security tips that really is what a high number of all kinds of web surfers do if they understand there is a risk that a scam artist may catch their poorly shielded passwords and get in their important documents.
dropbox encryption
It's a simple fact that even the youngest college child may have the ability to acquire access to the passwords of classmates, teachers, parents, and many others. Forgetting to take this into account is similar to believing:
That mindset isn't likely to assist you as soon as your password is outside in the open, your money disappears out of the bank account, somebody with your identity unexpectedly ends up having a huge debt which you're requested to cover, your documents abruptly look on Facebook or in your competitor, and also the suggestions and goods you really have been working so long time with are unexpectedly encouraged by somebody who fortunately discovered them on your documents.
So below are my online security suggestions about the best way best to safeguard your passwords.
Create your password as hard as possible to hack-
What exactly does this mean? At least ten digits are a mixture of numbers, symbols, and letters. It's significantly more challenging for hackers to crack a lengthy password using this mixture.
• Your passwords don't include your name, social security number, birthday, your bank account number, or any other private info.
• You'll be able to add a keyboard mix plus alternate with lower and upper case letters.
• Your password is something that you can remember but not easy for others to guess.
• Be careful where you maintain your passwords registered if they're hard to remember and the way you file them which means: Do not write your pin number for your debit/credit card using permanent ink onto the card.
|
{
"url": "https://www.bitbitbyte.com/online-safety-tips-how-to-protect-your-passwords/",
"source_domain": "www.bitbitbyte.com",
"snapshot_id": "crawl=CC-MAIN-2022-33",
"warc_metadata": {
"Content-Length": "44938",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:YDBCPFPCR4H4CH3PJBCBCRDVUKFCJLT3",
"WARC-Concurrent-To": "<urn:uuid:9a77bd97-ba8e-4774-8c56-ced2688a84a2>",
"WARC-Date": "2022-08-07T15:48:29Z",
"WARC-IP-Address": "198.7.57.210",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:DKA4IQPTNYYSVXPAFWG32HGQZOSOS2B7",
"WARC-Record-ID": "<urn:uuid:f867d78e-85fd-4f7f-a08d-fdcb7a496c81>",
"WARC-Target-URI": "https://www.bitbitbyte.com/online-safety-tips-how-to-protect-your-passwords/",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:f20000a6-abd2-460f-afba-74c6c5bd2c00>"
},
"warc_info": "isPartOf: CC-MAIN-2022-33\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for August 2022\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-66\r\nsoftware: Apache Nutch 1.18 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.4-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
168,
169,
220,
221,
555,
556,
593,
594,
850,
851,
870,
871,
1096,
1097,
1571,
1572,
1669,
1670,
1720,
1721,
1914,
1915,
2046,
2137,
2224
],
"line_end_idx": [
168,
169,
220,
221,
555,
556,
593,
594,
850,
851,
870,
871,
1096,
1097,
1571,
1572,
1669,
1670,
1720,
1721,
1914,
1915,
2046,
2137,
2224,
2441
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 2441,
"ccnet_original_nlines": 25,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.4270152449607849,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.13071894645690918,
"rps_doc_frac_unique_words": 0.5721649527549744,
"rps_doc_mean_word_length": 5.092783451080322,
"rps_doc_num_sentences": 16,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 5.06710147857666,
"rps_doc_word_count": 388,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.032894741743803024,
"rps_doc_frac_chars_top_3gram": 0.018218619748950005,
"rps_doc_frac_chars_top_4gram": 0,
"rps_doc_books_importance": -249.423095703125,
"rps_doc_books_importance_length_correction": -249.423095703125,
"rps_doc_openwebtext_importance": -137.3436279296875,
"rps_doc_openwebtext_importance_length_correction": -137.3436279296875,
"rps_doc_wikipedia_importance": -92.66920471191406,
"rps_doc_wikipedia_importance_length_correction": -92.66920471191406
},
"fasttext": {
"dclm": 0.03850216045975685,
"english": 0.947134256362915,
"fineweb_edu_approx": 2.1154778003692627,
"eai_general_math": 0.005908910185098648,
"eai_open_web_math": 0.09088116884231567,
"eai_web_code": 0.0014795700553804636
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.82",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "363.12",
"labels": {
"level_1": "Social sciences",
"level_2": "Social service and Societies",
"level_3": "Political activists"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "10",
"label": "Knowledge Article"
},
"secondary": {
"code": "23",
"label": "Tutorial"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "1",
"label": "General Audience"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-2,084,528,012,474,662,000
|
Windows could not parse or process the unattend answer file for pass [specialize]
I was at a customer which I have deployed vCloud Automation Center 6.1 for, and they tried to create a new blueprint. They have copied the old blueprint and only changed the VM template used in that blueprint from Windows 2012 to Windows 2008 R2. They saved and published the new blueprint without any problem, then they tried to deploy the new blueprint. The blueprint deployment kept failing with the following error:
“Request failed: Machine VTTestVM001: Timeout customizing machine”
From the error, I was able to tell it was getting stuck at the guest customization stage, so I deployed one more VM and waited till it get to the guest customization stage, then opened a console to the VM to be greeted with the following Sysprep error:
Windows could not parse or process the unattend answer file for pass [specialize]. The settings specified in the answer file cannot be applied. The error was detected while processing settings for component [Microsoft-Windows-Shell-Setup]”
Below is a screenshot showing the actual error on screen:
Windows could not parse or process the unattend answer file or pass [specialize]
After I hit OK, the machine restarted again and gave the following error and kept repetitively restarting and giving the same error afterword:
“The computer restarted unexpectedly or encountered an unexpected error.Read More
|
{
"url": "https://www.virtualizationteam.com/tag/sysprep",
"source_domain": "www.virtualizationteam.com",
"snapshot_id": "crawl=CC-MAIN-2022-40",
"warc_metadata": {
"Content-Length": "36948",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:UZC26GNI6BZZDYUVBLLHDENHGTS5AOUH",
"WARC-Concurrent-To": "<urn:uuid:ad192e1e-8925-434c-9a00-4821f6096d66>",
"WARC-Date": "2022-09-29T04:41:43Z",
"WARC-IP-Address": "192.254.146.202",
"WARC-Identified-Payload-Type": "application/xhtml+xml",
"WARC-Payload-Digest": "sha1:CIVF7GZX2F6LSKJS6XD6Z2Q5GDAA6DA6",
"WARC-Record-ID": "<urn:uuid:48601b2a-57ce-40f4-aee9-cb654900d42c>",
"WARC-Target-URI": "https://www.virtualizationteam.com/tag/sysprep",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:f2842b1d-b777-4e25-b233-a5f6a09292ed>"
},
"warc_info": "isPartOf: CC-MAIN-2022-40\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for September/October 2022\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-88\r\nsoftware: Apache Nutch 1.19 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.4-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
82,
83,
503,
504,
571,
572,
826,
827,
1067,
1068,
1126,
1127,
1208,
1209,
1352,
1353
],
"line_end_idx": [
82,
83,
503,
504,
571,
572,
826,
827,
1067,
1068,
1126,
1127,
1208,
1209,
1352,
1353,
1434
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 1434,
"ccnet_original_nlines": 16,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3909774422645569,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.03759397938847542,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.13533835113048553,
"rps_doc_frac_unique_words": 0.5152838230133057,
"rps_doc_mean_word_length": 5.096069812774658,
"rps_doc_num_sentences": 8,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.425539016723633,
"rps_doc_word_count": 229,
"rps_doc_frac_chars_dupe_10grams": 0.15766924619674683,
"rps_doc_frac_chars_dupe_5grams": 0.15766924619674683,
"rps_doc_frac_chars_dupe_6grams": 0.15766924619674683,
"rps_doc_frac_chars_dupe_7grams": 0.15766924619674683,
"rps_doc_frac_chars_dupe_8grams": 0.15766924619674683,
"rps_doc_frac_chars_dupe_9grams": 0.15766924619674683,
"rps_doc_frac_chars_top_2gram": 0.03427591919898987,
"rps_doc_frac_chars_top_3gram": 0.0385604090988636,
"rps_doc_frac_chars_top_4gram": 0.0514138787984848,
"rps_doc_books_importance": -132.5767822265625,
"rps_doc_books_importance_length_correction": -130.2519989013672,
"rps_doc_openwebtext_importance": -62.22904586791992,
"rps_doc_openwebtext_importance_length_correction": -62.22904586791992,
"rps_doc_wikipedia_importance": -43.099117279052734,
"rps_doc_wikipedia_importance_length_correction": -36.05269241333008
},
"fasttext": {
"dclm": 0.404449999332428,
"english": 0.9161525368690491,
"fineweb_edu_approx": 1.8261827230453491,
"eai_general_math": 0.8013366460800171,
"eai_open_web_math": 0.17447030544281006,
"eai_web_code": 0.9468523263931274
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.446",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.162",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "1",
"label": "Truncated Snippets"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "16",
"label": "Personal Blog"
},
"secondary": {
"code": "21",
"label": "Customer Support"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "4",
"label": "Graduate/Expert Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
1,990,337,871,005,882,000
|
What is #vulnerability management? #Processes and #software for #prioritizing #threats
Organizations handle vulnerability management in various ways, from training and best-practice implementations to filtering out all but the most dangerous threats. Here’s a look at some of today’s more innovative solutions.
Vulnerability management is the process of staying on top of vulnerabilities so the fixes can be more frequent and effective. Vulnerabilities in need of fixing must be prioritized based on which ones post the most immediate risk to the network. It’s handled in various ways by security companies working in the field, from training and best-practice implementations to filtering all the vulnerability noise down to just the most dangerous threats for a protected organization.
In cybersecurity, vulnerabilities are a big deal because without them, there would be very few breaches. But vulnerabilities on their own aren’t active threats, so it’s difficult for companies to figure out which to address, and in what order. This is especially true when the number of vulnerabilities climb to staggering levels — sometimes into the millions for larger networks.
Think of vulnerabilities like holes in a suit of armor. The holes might not instantly pose a problem, but probably will cause trouble eventually. Ideally, patching those holes before someone exploits one, sending an arrow through it for example, is a good idea. The problem in cybersecurity is that there are a lot of vulnerabilities.
Almost anything can become a vulnerability and thus a liability to network security. Things like unpatched operating systems, or programs and apps running old software versions are common vulnerabilities, as are siloed applications plugged into a modern network. On the more advanced side, attackers may find exploits that nobody else knows about, attacking a hole in the armor that was previously unknown. Even users can sometimes be considered vulnerabilities, especially today when many of the most targeted attacks, such as phishing, are designed to trick users into lowering the defenses for attackers.
. . . . . . . .
Leave a Reply
|
{
"url": "https://nationalcybersecurity.com/vulnerability-management-processes-software-prioritizing-threats/",
"source_domain": "nationalcybersecurity.com",
"snapshot_id": "crawl=CC-MAIN-2019-30",
"warc_metadata": {
"Content-Length": "54239",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:WBQ5FCAAKZVT3PZM6G7AYESAK24OIU6P",
"WARC-Concurrent-To": "<urn:uuid:b9490177-b97d-4fb9-b18b-478fcd03e1e0>",
"WARC-Date": "2019-07-16T06:31:51Z",
"WARC-IP-Address": "87.106.192.188",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:FKKBKMZAEY4SRNOJYOLLQKKDDYT3TJRB",
"WARC-Record-ID": "<urn:uuid:1998f5de-0172-4cd2-8ab5-1a7c74d3ea58>",
"WARC-Target-URI": "https://nationalcybersecurity.com/vulnerability-management-processes-software-prioritizing-threats/",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:a543fd52-94cd-4c69-bcd5-bdcf50ce49cc>"
},
"warc_info": "isPartOf: CC-MAIN-2019-30\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for July 2019\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-144-233-243.ec2.internal\r\nsoftware: Apache Nutch 1.15 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.1-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
87,
88,
312,
313,
790,
791,
1172,
1173,
1508,
1509,
2117,
2118,
2134,
2135
],
"line_end_idx": [
87,
88,
312,
313,
790,
791,
1172,
1173,
1508,
1509,
2117,
2118,
2134,
2135,
2148
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 2148,
"ccnet_original_nlines": 14,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.45854923129081726,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.1424870491027832,
"rps_doc_frac_unique_words": 0.5753846168518066,
"rps_doc_mean_word_length": 5.415384769439697,
"rps_doc_num_sentences": 18,
"rps_doc_symbol_to_word_ratio": 0.012953369878232479,
"rps_doc_unigram_entropy": 4.8898444175720215,
"rps_doc_word_count": 325,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.06022727116942406,
"rps_doc_frac_chars_dupe_6grams": 0.06022727116942406,
"rps_doc_frac_chars_dupe_7grams": 0.06022727116942406,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.015909090638160706,
"rps_doc_frac_chars_top_3gram": 0.014772729948163033,
"rps_doc_frac_chars_top_4gram": 0.030681820586323738,
"rps_doc_books_importance": -165.581298828125,
"rps_doc_books_importance_length_correction": -165.581298828125,
"rps_doc_openwebtext_importance": -99.11856842041016,
"rps_doc_openwebtext_importance_length_correction": -99.11856842041016,
"rps_doc_wikipedia_importance": -44.878543853759766,
"rps_doc_wikipedia_importance_length_correction": -44.878543853759766
},
"fasttext": {
"dclm": 0.04911268129944801,
"english": 0.9488900303840637,
"fineweb_edu_approx": 2.3675670623779297,
"eai_general_math": 0.34975409507751465,
"eai_open_web_math": 0.42370539903640747,
"eai_web_code": 0.025829849764704704
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.82",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.02",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "1",
"label": "Truncated Snippets"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "10",
"label": "Knowledge Article"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
3,126,386,700,032,882,700
|
返回列表
canvas中绘制图片源的src发生改变后,绘图会变为空白
默认分类 2015/11/07 05:45
canvas中绘制图片源的src发生改变后,绘图会变为空白
解决方法是: 先删除原来的图片,再创建一张一模一样的图片。
下面这段代码是修复后的代码
var origin = document.getElementById(pid + 'Origin');
var parentNode = origin.parentNode;
parentNode.removeChild(origin);
origin = document.createElement('img');
origin.className = 'img-origin';
origin.src = reader.result;
origin.id = pid + 'Origin';
parentNode.appendChild(origin);
其对应修复前有问题的代码如下
var origin = document.getElementById(pid + 'Origin');
origin.src = reader.result;
全部代码
<!DOCTYPE html>
<html>
<head>
<title>洋码头-上传身份证</title>
<meta charset="utf-8" />
<meta name="viewport" content="initial-scale=1, maximum-scale=1, user-scalable=no" />
<meta name="format-detection" content="telephone=no" />
<script src="/ymt_core.69d806bac3.js"></script>
<script src="/zepto.08084123f2.js"></script>
<script type="text/javascript">
'use strict';
var hui = window.hui = window.hui ? window.hui : {};
hui.loadjs = function (url) {
// 容错处理
if (!url) {
return window.console.log('hui.loadjs(url): url is null');
}
// 一次加载多个
if (Object.prototype.toString.call(url) === '[object Array]') {
for (var i = 0, len = url.length; i < len; i++) {
hui.loadjs(url[i]);
}
return;
}
// 开始加载
if (hui.loadjs.loaded && hui.loadjs.loaded[url]) return;
hui.loadjs.loaded = hui.loadjs.loaded || {};
hui.loadjs.loaded[url] = true;
var env = 'evt';
var s = document.createElement('script');
url = window.location.href.indexOf('startDebug=true') !== -1 && url.indexOf('/_sourcemap.') === -1 ?
url.replace(/\.[a-z0-9]{10}\.js/, '.js') : url;
s.src = url + ((env === 'dev' && window.location.href.indexOf('stopDev=true') === -1) || window.location.href.indexOf('startDev=true') !== -1 ? '?' + (new Date().getTime()) : '');
document.documentElement.appendChild(s);
};
// 本地模块及外部模块
window.sourcemap_local = window.sourcemap_local || {};
window.sourcemap_third = window.sourcemap_third || {};
// 自动加载依赖模块
hui.define_autoload = true;
hui.staticDomain = '';
// 基础模块初始化结束后的回调
hui.loadNextCallback = [];
hui.onDefineReady = function (callback) {
(hui.loadNextLoaded ? callback() : hui.loadNextCallback.push(callback));
};
// hui.onDefineReady 示例
hui.onDefineReady(function (callback) {
hui.showLog = function (msg, opt) {
opt = opt || {};
var outputlog = document.getElementById('outputlog');
var outputlogtxt = document.getElementById('outputlogtxt');
if (!outputlog) {
var str = '<div id="outputlog" onclick="this.style.display=\'none\'" style="position: fixed;z-index: 2000;width: 80%;height: 80%;left: 10%;top: 5%;word-break: break-all;"></div>';
var node = document.createElement('DIV');
node.innerHTML = str;
for (var i = 0, len = node.children.length; i < len; i++) {
document.documentElement.appendChild(node.children[i]);
}
node = undefined;
outputlog = document.getElementById('outputlog');
}
if (outputlog) {
var outputlogtxt = outputlog.getElementsByTagName('strong')[0];
if (outputlogtxt) {
outputlogtxt.innerHTML = msg;
}
else {
outputlog.innerHTML = ['<table style="width: 100%;height: 100%;"><tbody><tr><td style="vertical-align: middle;text-align: center;">',
'<strong style="font-weight:normal; display: inline-block;background-color: black;color: white;opacity: 0.75;padding: 1.5rem 1rem;border-radius: 10px;font-size: 1.3rem;">',
msg,
'</strong></td></tr></tbody></table></div>'
].join('');
}
outputlog.style.display = 'block';
}
if (String(opt.time) !== '-1') {
if (outputlog.timer) {
window.clearTimeout(outputlog.timer);
}
outputlog.timer = window.setTimeout(function () {
var a = document.getElementById('outputlog');
a && (a.style.display = 'none');
a.timer = null;
opt.onclose && opt.onclose();
}, opt.time || 3000);
}
};
});
</script>
<script type="text/javascript">
'use strict';
(function (doc, win) {
// 分辨率Resolution适配
var docEl = doc.documentElement,
resizeEvt = 'orientationchange' in window ? 'orientationchange' : 'resize',
recalc = function () {
var clientWidth = docEl.clientWidth;
if (!clientWidth) return;
docEl.style.fontSize = 10 * (clientWidth / 320) + 'px';
};
// Abort if browser does not support addEventListener
if (!doc.addEventListener) return;
win.addEventListener(resizeEvt, recalc, false);
doc.addEventListener('DOMContentLoaded', recalc, false);
// 一物理像素在不同屏幕的显示效果不一样。要根据devicePixelRatio来修改meta标签的scale,要注释上面的meta标签
(function () {
//return;
var dpr = 0;
var isIPhone = win.navigator.appVersion.match(/iphone/gi);
var devicePixelRatio = win.devicePixelRatio;
if (isIPhone) {
// iOS下,对于2和3的屏,用2倍的方案,其余的用1倍方案
if (devicePixelRatio >= 3 && (!dpr || dpr >= 3)) {
dpr = 3;
}
else if (devicePixelRatio >= 2 && (!dpr || dpr >= 2)) {
dpr = 2;
}
else {
dpr = 1;
}
}
else {
// 其他设备下,仍旧使用1倍的方案
dpr = 1;
}
var scale = 1 / dpr;
//
var metaEl = '';
metaEl = doc.createElement('meta');
metaEl.setAttribute('name', 'viewport');
metaEl.setAttribute('content', 'initial-scale=' + scale + ', maximum-scale=' + scale + ', minimum-scale=' + scale + ', user-scalable=no');
if (docEl.firstElementChild) {
docEl.firstElementChild.appendChild(metaEl);
}
else {
var wrap = doc.createElement('div');
wrap.appendChild(metaEl);
doc.write(wrap.innerHTML);
}
})();
})(document, window);
</script>
<link rel="stylesheet" href="/home.css">
<style>
</style>
</head>
<body>
<div class="wrapper">
<h3 class="top-title">洋码头-上传身份证</h3>
<div class="user-tip">
你所提供的信息均将加密,安全可靠。
<!--a href="#description">查看详情></a-->
</div>
<div class="section section-first">
<div class="section-title">收件人</div>
<div class="section-content" id="userWrap">
<div class="username" id="username" Name="但是" Mobile="13811111111" UserId="4085" AccessToken="276827AB97D367A6662BB8A46D4A6A828980C19A4654A5DE117CF54F3CA96BDE798AA5B04F276D9F9C27D205698F300463954DCAEA8B27DB" OrderId="" AddressId="764722">但是(联系电话:13811111111)</div>
</div>
</div>
<div class="section">
<div class="section-title">收件人身份证号</div>
<div class="section-subtitle">务必与所选收件人相匹配</div>
<div class="section-content">
<input type="text" name="CardNumber" id="CardNumber" maxlength="18" class="input-text" value="">
</div>
</div>
<!--div class="section">
<button onclick="testAndroidCallback()">testAndroidCallback</button>
</div-->
<div class="section">
<div class="section-title">收件人身份证照片</div>
<div class="section-subtitle">需横屏拍摄,务必成像清晰
</div>
<div class="section-content">
<div class="row">
<div class="cell-left">
<img src="data:image/gif;base64,R0lGODlhAQABAIAAAP///wAAACH5BAEAAAAALAAAAAABAAEAAAICRAEAOw==" class="sample-front">
<br/>正面样例
</div>
<div class="cell-right">
<div class="img-add">
<input type="file" name="RightSide" id="RightSide" index="1" multiple123="multiple" class="file-input" ontouchend="this.onclick='';page.chooseImage(this)" onclick="page.chooseImage(this)" onchange="page.previewImage(this)" />
<button class="btn-add" id="RightSideBtn">选择</button>
<button class="btn-rotate" onclick="rotateImg('RightSide')" >转向</button>
</div>
<div class="img-front">
<img src="/idcard-1.jpg" alt="" class="img-upload" id="RightSidePreview" url="" />
<img src="data:image/gif;base64,R0lGODlhAQABAIAAAP///wAAACH5BAEAAAAALAAAAAABAAEAAAICRAEAOw==" alt="" class="img-origin" id="RightSideOrigin" />
</div>
</div>
</div>
<div class="row">
<div class="cell-left">
<img src="data:image/gif;base64,R0lGODlhAQABAIAAAP///wAAACH5BAEAAAAALAAAAAABAAEAAAICRAEAOw==" class="sample-back">
<br/>背面样例
</div>
<div class="cell-right">
<div class="img-add">
<input type="file" name="ReverseSide" id="ReverseSide" index="1" multiple123="multiple" class="file-input" ontouchend="this.onclick='';page.chooseImage(this)" onclick="page.chooseImage(this)" onchange="page.previewImage(this)" />
<button class="btn-add" id="ReverseSideBtn">选择</button>
<button class="btn-rotate" onclick="rotateImg('ReverseSide')">转向</button>
</div>
<div class="img-front">
<img src="/idcard-2.jpg" alt="" class="img-upload" id="ReverseSidePreview" url="" />
<img src="data:image/gif;base64,R0lGODlhAQABAIAAAP///wAAACH5BAEAAAAALAAAAAABAAEAAAICRAEAOw==" alt="" class="img-origin" id="ReverseSideOrigin" />
</div>
</div>
</div>
</div>
</div>
<canvas id="myCanvas" width="1" height="1" style="border:0px solid #c3c3c3;"></canvas>
<div class="section-action">
<button class="btn-upload" id="btnSubmit" onclick="page.saveIdCardInfo()">上 传</button>
</div>
</div>
<script type="text/javascript">
'use strict';
var Ymt;
var page = {};
window.onload = function () {
var RightSide = document.getElementById('RightSide');
var ReverseSide = document.getElementById('ReverseSide');
var RightSideBtn = document.getElementById('RightSideBtn');
var ReverseSideBtn = document.getElementById('ReverseSideBtn');
if (window.Ymt && Ymt.chooseImage) {
RightSide.style.display = 'none';
ReverseSide.style.display = 'none';
RightSideBtn.ontouchend = RightSide.ontouchend;
RightSideBtn.onclick = RightSide.onclick;
ReverseSideBtn.ontouchend = ReverseSide.ontouchend;
ReverseSideBtn.onclick = ReverseSide.onclick;
}
if (document.getElementById('myCanvas').getContext) {
page.initCanvas('RightSide');
page.initCanvas('ReverseSide');
}
};
page.initCanvas = function (pid) {
var preview = document.getElementById(pid + 'Preview');
var fileinput = document.getElementById(pid);
var index = parseInt(fileinput.getAttribute('index'), 10);
var result = document.getElementById(pid + 'Result');
result && preview.parentNode.removeChild(result);
result = document.createElement('canvas');
result.setAttribute('id', pid + 'Result');
result.className = 'img-result';
result.width = 800;
result.height = 600;
preview.parentNode.insertBefore(result, preview);
fileinput.setAttribute('index', index);
};
page.checkIdCardInfo = function () {
var CardNumber = document.getElementById('CardNumber').value;
if (!page.checkIdCode(CardNumber)) {
hui.showLog('您输入的身份证格式有误,<br/>请确认后重新输入');
return false;
}
return true;
};
/**
* @method checkIdCardPhoto
* @description 检查身份证图片
*/
page.checkIdCardPhoto = function () {
var RightSide = document.getElementById('RightSide');
var ReverseSide = document.getElementById('ReverseSide');
if ((RightSide.getAttribute('url') || (RightSide.files && RightSide.files.length)) &&
(ReverseSide.getAttribute('url') || (ReverseSide.files && ReverseSide.files.length))) {
return true;
}
hui.showLog('身份证图片不能为空');
return false;
};
/**
* @method getParamMap
* @description 获取数据
*/
page.getParamMap = function () {
var username = document.getElementById('username');
var result = {};
result.Name = hui.Control.decode(username.getAttribute('Name') || '');
result.Mobile = hui.Control.decode(username.getAttribute('Mobile') || '');
result.UserId = hui.Control.decode(username.getAttribute('UserId') || '');
result.AccessToken = hui.Control.decode(username.getAttribute('AccessToken') || '');
result.OrderId = hui.Control.decode(username.getAttribute('OrderId') || '');
result.AddressId = hui.Control.decode(username.getAttribute('AddressId') || '');
result.CardNumber = document.getElementById('CardNumber').value;
result.Status = 0; // 0:待审核
result.HasPic = 1; // 1:有图片
result.BuyerId = result.UserId;
result.Operater = result.UserId;
result.CardType = 1; // 1:身份证
var RightSide = document.getElementById('RightSide');
var ReverseSide = document.getElementById('ReverseSide');
result.RightSide = RightSide.getAttribute('url');
result.ReverseSide = ReverseSide.getAttribute('url');
return result;
};
/**
* @method saveIdCardInfo
* @description 提交数据到服务端
*/
page.saveIdCardInfo = function () {
if (!document.getElementById('btnSubmit').disabled && page.checkIdCardInfo() && page.checkIdCardPhoto() && window.FormData) {
page.updateBtnStatus('disabled');
if (window.Ymt && Ymt.chooseImage) {
page.saveIdCardInfoData();
}
else {
if (document.getElementById('myCanvas').getContext) {
page.uploadBase64Image('RightSide', function (url) {
document.getElementById('RightSide').setAttribute('url', url);
page.uploadBase64Image('ReverseSide', function (url) {
document.getElementById('ReverseSide').setAttribute('url', url);
page.saveIdCardInfoData();
});
});
}
else {
page.uploadSingleImage(document.getElementById('RightSide').files[0], function (url) {
document.getElementById('RightSide').setAttribute('url', url);
page.uploadSingleImage(document.getElementById('ReverseSide').files[0], function (url) {
document.getElementById('ReverseSide').setAttribute('url', url);
page.saveIdCardInfoData();
});
});
}
}
}
};
page.saveIdCardInfoData = function () {
var result = page.getParamMap();
var formData = new FormData();
for (var i in result) {
formData.append(i, result[i]);
}
var xhr = new XMLHttpRequest();
xhr.open('POST', '/forBuyerApp/api/saveIdCardInfo');
// 定义上传完成后的回调函数
xhr.onload = function (res) {
if (xhr.status === 200) {
var data = (new Function('return ' + res.target.responseText))();
if (data && data.Code == 200 && data.Data && data.Data.IsSuccess) {
hui.showLog('身份证上传成功', {
time: 3000,
onclose: function () {
window.location.href = '/forBuyerApp/goOver';
}
});
page.updateBtnStatus();
}
else {
hui.showLog(data && data.Data && data.Data.Message ? data.Data.Message : '身份证上传失败', {
time: 4000
});
page.updateBtnStatus();
}
}
else {
hui.showLog('身份证上传失败', {
time: 4000
});
page.updateBtnStatus();
}
};
xhr.send(formData);
};
// {"Msg":"上传成功","Status":200,"Result":{"idCardPic":"http://pm2.img.ymatou.com/G01/upload/product/original/M00/07/C6/rBBlD1Yxy-WANEQ2AAcEWMJPnYo454_o.jpg"} }
page.uploadSingleImage = function (file, next) {
var formData = new FormData();
formData.append('idCardPic', file);
var xhr = new XMLHttpRequest();
xhr.open('POST', '/forBuyerApp/api/saveIdCardPhoto');
// 定义上传完成后的回调函数
xhr.onload = function (res) {
if (xhr.status === 200) {
var data = (new Function('return ' + res.target.responseText))();
if (data && data.Status === 200 && data.Result && data.Result.idCardPic) {
next && next(data.Result.idCardPic);
}
else {
hui.showLog('身份证上传失败,请稍后重试');
// next && next();
page.updateBtnStatus();
}
}
else {
hui.showLog('网络错误,请稍后重试');
// next && next();
page.updateBtnStatus();
}
};
xhr.send(formData);
};
page.uploadBase64Image = function (pid, next) {
var imgBase64 = document.getElementById(pid + 'Preview').src;
var formData = new FormData();
formData.append('idCardPicBase64', imgBase64);
var xhr = new XMLHttpRequest();
xhr.open('POST', '/forBuyerApp/api/saveIdCardPhotoBase64');
// 定义上传完成后的回调函数
xhr.onload = function (res) {
if (xhr.status === 200) {
var data = (new Function('return ' + res.target.responseText))();
if (data && data.Status === 200 && data.Result && data.Result.idCardPic) {
next && next(data.Result.idCardPic);
}
else {
hui.showLog('身份证上传失败,请稍后重试');
// next && next();
page.updateBtnStatus();
}
}
else {
hui.showLog('网络错误,请稍后重试');
// next && next();
page.updateBtnStatus();
}
};
xhr.send(formData);
};
page.updateBtnStatus = function (status) {
var disabled = status === 'disabled' ? 'disabled' : '';
var btnSubmit = document.getElementById('btnSubmit');
btnSubmit.disabled = disabled;
btnSubmit.innerHTML = disabled ? '上传中...' : '上 传';
};
/**
* @method previewImage
* @description IOS下预览图片
*/
page.previewImage = function (elem) {
if (typeof (FileReader) === 'undefined') {
console.log('抱歉,你的浏览器不支持 FileReader,请使用现代浏览器操作!');
}
else {
var pid = elem.id;
var file = elem.files[0];
var reader = new FileReader();
reader.readAsDataURL(file);
reader.onload = function (e) {
var preview = document.getElementById(pid + 'Preview');
preview.src = reader.result;
var origin = document.getElementById(pid + 'Origin');
var parentNode = origin.parentNode;
parentNode.removeChild(origin);
origin = document.createElement('img');
origin.className = 'img-origin';
origin.src = reader.result;
origin.id = pid + 'Origin';
parentNode.appendChild(origin);
elem.setAttribute('choosed', '1');
};
}
};
page.uploading = false;
page.chooseImage = function (elem) {
if (window.Ymt && Ymt.chooseImage && !page.uploading) {
page.uploading = true;
window.setTimeout(function () {
page.uploading = false;
}, 1500);
window.currentFile = elem.id.replace('Btn', '');
var UserId = document.getElementById('username').getAttribute('UserId');
Ymt.chooseImage('{url:"http://id.m.ymatou.com/forBuyerApp/api/saveIdCardPhoto", userId:"' + UserId + '"}');
}
};
window.currentFile = 'RightSide';
// {"Msg":"上传成功","Status":200,"Result":{"idCardPic":"http://pm5.img.ymatou.com/G01/upload/product/original/M00/07/B4/rBBlD1YwbpmAc9OtAAEsLR7DFbE676_o.jpg"} }
function onCallBack(ret) {
if (!ret) {
return;
}
try {
ret = String(ret).replace(/\\/ig, '\\\\');
ret = JSON.parse(ret);
if (ret && ret.Result && ret.Result.idCardPic) {
var url = ret.Result.idCardPic;
var previewImage = document.getElementById(window.currentFile + 'Preview');
previewImage.src = url;
var currentFile = document.getElementById(window.currentFile);
currentFile.setAttribute('url', url);
return;
}
hui.showLog('上传失败');
}
catch (e) {
hui.showLog(e);
}
}
// 测试Android下保存
function testAndroidCallback() {
window.Ymt = {};
Ymt.chooseImage = 1;
window.currentFile = 'RightSide';
onCallBack('{"Msg":"上传成功","Status":200,"Result":{"idCardPic":"http://pm5.img.ymatou.com/G01/upload/product/original/M00/07/B4/rBBlD1YwbpmAc9OtAAEsLR7DFbE676_o.jpg"} }');
window.currentFile = 'ReverseSide';
onCallBack('{"Msg":"上传成功","Status":200,"Result":{"idCardPic":"http://pm5.img.ymatou.com/G01/upload/product/original/M00/07/B4/rBBlD1YwbpmAc9OtAAEsLR7DFbE676_o.jpg"} }');
}
/**
* @function 解析地址栏参数
*/
page.parseLocator = function (url) {
url = url === null || url === undefined ? window.location.href : String(url);
var pair,
query = {},
loc = '',
args = '',
list,
v,
str = url.split('#');
if (~url.indexOf('?')) {
// Parse ?aa=xxx
pair = str[0].match(/^([^\?]*)(\?(.*))?$/);
if (pair) {
//loc = pair[1];
args = (pair.length == 4 ? pair[3] : '') || '';
}
list = args ? args.split('&') : [];
for (var i = 0, len = list.length; i < len; i++) {
v = list[i].split('=');
v.push('');
query[v[0]] = decodeURIComponent(v[1]);
}
}
return {
'location': loc,
'query': query
};
};
/**
* @class 身份证校验
*/
page.checkIdCode = (function () {
/**
* 身份证15位编码规则:dddddd yymmdd xx p
* dddddd:地区码
* yymmdd: 出生年月日
* xx: 顺序类编码,无法确定
* p: 性别,奇数为男,偶数为女
* <p />
* 身份证18位编码规则:dddddd yyyymmdd xxx y
* dddddd:地区码
* yyyymmdd: 出生年月日
* xxx:顺序类编码,无法确定,奇数为男,偶数为女
* y: 校验码,该位数值可通过前17位计算获得
* <p />
* 18位号码加权因子为(从右到左) Wi = [ 7, 9, 10, 5, 8, 4, 2, 1, 6, 3, 7, 9, 10, 5, 8, 4, 2,1 ]
* 验证位 Y = [ 1, 0, 10, 9, 8, 7, 6, 5, 4, 3, 2 ]
* 校验位计算公式:Y_P = mod( ∑(Ai×Wi),11 )
* i为身份证号码从右往左数的 2...18 位; Y_P为脚丫校验码所在校验码数组位置
*
*/
var Wi = [7, 9, 10, 5, 8, 4, 2, 1, 6, 3, 7, 9, 10, 5, 8, 4, 2, 1]; // 加权因子
var ValideCode = [1, 0, 10, 9, 8, 7, 6, 5, 4, 3, 2]; // 身份证验证位值.10代表X
function IdCardValidate(idCard) {
idCard = idCard.replace(/ /g, '').replace(/(^\s*)|(\s*$)/g, '');
if (idCard.length == 15) {
return isValidityBrithBy15IdCard(idCard);
}
else if (idCard.length == 18) {
var a_idCard = idCard.split(''); // 得到身份证数组
if (isValidityBrithBy18IdCard(idCard) && isTrueValidateCodeBy18IdCard(a_idCard)) {
return true;
}
else {
return false;
}
}
else {
return false;
}
}
/**
* 判断身份证号码为18位时最后的验证位是否正确
* @@param a_idCard 身份证号码数组
* @@return
*/
function isTrueValidateCodeBy18IdCard(a_idCard) {
var sum = 0; // 声明加权求和变量
if (a_idCard[17].toLowerCase() == 'x') {
a_idCard[17] = 10; // 将最后位为x的验证码替换为10方便后续操作
}
for (var i = 0; i < 17; i++) {
sum += Wi[i] * a_idCard[i]; // 加权求和
}
var valCodePosition = sum % 11; // 得到验证码所位置
if (a_idCard[17] == ValideCode[valCodePosition]) {
return true;
}
else {
return false;
}
}
/**
* 验证18位数身份证号码中的生日是否是有效生日
* @@param idCard 18位书身份证字符串
* @@return
*/
function isValidityBrithBy18IdCard(idCard18) {
var year = idCard18.substring(6, 10);
var month = idCard18.substring(10, 12);
var day = idCard18.substring(12, 14);
var temp_date = new Date(year, parseFloat(month) - 1, parseFloat(day));
// 这里用getFullYear()获取年份,避免千年虫问题
if (temp_date.getFullYear() != parseFloat(year) || temp_date.getMonth() != parseFloat(month) - 1 || temp_date.getDate() != parseFloat(day)) {
return false;
}
else {
return true;
}
}
/**
* 验证15位数身份证号码中的生日是否是有效生日
* @@param idCard15 15位书身份证字符串
* @@return
*/
function isValidityBrithBy15IdCard(idCard15) {
var year = idCard15.substring(6, 8);
var month = idCard15.substring(8, 10);
var day = idCard15.substring(10, 12);
var temp_date = new Date(year, parseFloat(month) - 1, parseFloat(day));
// 对于老身份证中的你年龄则不需考虑千年虫问题而使用getYear()方法
if (temp_date.getYear() != parseFloat(year) || temp_date.getMonth() != parseFloat(month) - 1 || temp_date.getDate() != parseFloat(day)) {
return false;
}
else {
return true;
}
}
return function (cardId) {
if (cardId === null || cardId === '') {
return false;
}
else {
if (!IdCardValidate(cardId)) {
return false;
}
else {
return true;
}
}
};
})();
</script>
<br/>
<script>
'use strict';
function rotateImg(pid, step) {
var elem = document.getElementById(pid);
if (!elem.getAttribute('choosed')) return;
var origin = document.getElementById(pid + 'Origin');
origin.crossOrigin = '*';
//img的高度和宽度不能在img元素隐藏后获取,否则会出错
step = step ? step : (origin.getAttribute('step') || 0);
++step && step > 3 && (step = 0);
origin.setAttribute('step', step);
var scene = document.getElementById(pid + 'Result');
// //旋转角度以弧度值为参数
var ctx2 = scene.getContext('2d');
ctx2.clearRect(0, 0, scene.width, scene.height);
ctx2.save(); //保存画笔状态
if (step === 1) {
ctx2.rotate(90 * Math.PI / 180);
ctx2.drawImage(origin, 0, 0, origin.width, origin.height, 0, -scene.width, scene.height, scene.width);
}
else if (step === 2) {
ctx2.rotate(180 * Math.PI / 180);
ctx2.drawImage(origin, 0, 0, origin.width, origin.height, -scene.width, -scene.height, scene.width, scene.height);
}
else if (step === 3) {
ctx2.rotate(270 * Math.PI / 180);
ctx2.drawImage(origin, 0, 0, origin.width, origin.height, -scene.height, 0, scene.height, scene.width);
}
else if (step === 0) {
ctx2.rotate(0 * Math.PI / 180);
ctx2.drawImage(origin, 0, 0, origin.width, origin.height, 0, 0, scene.width, scene.height);
}
ctx2.restore(); //绘制结束以后,恢复画笔状态
document.getElementById(pid + 'Preview').src = scene.toDataURL();
}
</script>
<!-- target: footer -->
</body>
</html>
|
{
"url": "http://haiyang.me/read.php?key=614",
"source_domain": "haiyang.me",
"snapshot_id": "crawl=CC-MAIN-2019-13",
"warc_metadata": {
"Content-Length": "34296",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:5PKONPORCSLGUEIZC5CRFRUL6BSGPGXY",
"WARC-Concurrent-To": "<urn:uuid:a1393a01-e613-4c5a-912a-4a5816d5bf3b>",
"WARC-Date": "2019-03-20T01:13:55Z",
"WARC-IP-Address": "166.62.10.28",
"WARC-Identified-Payload-Type": "application/xhtml+xml",
"WARC-Payload-Digest": "sha1:ZTHWSZYNOUQOBKUKEFSGHIBQ75AMBMKN",
"WARC-Record-ID": "<urn:uuid:39c552e9-da03-45c7-8a4c-51312759e0d8>",
"WARC-Target-URI": "http://haiyang.me/read.php?key=614",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:4556eae0-27d5-4a15-9088-2b6ad1094949>"
},
"warc_info": "isPartOf: CC-MAIN-2019-13\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for March 2019\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-171-229-147.ec2.internal\r\nsoftware: Apache Nutch 1.15 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 0.11-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
5,
6,
36,
37,
59,
60,
90,
91,
121,
122,
136,
137,
191,
227,
259,
260,
300,
333,
361,
389,
421,
422,
437,
438,
492,
520,
521,
526,
527,
543,
550,
551,
558,
583,
608,
694,
750,
798,
843,
875,
889,
942,
943,
973,
985,
1001,
1068,
1074,
1088,
1156,
1214,
1246,
1256,
1272,
1278,
1290,
1351,
1400,
1435,
1436,
1457,
1503,
1608,
1664,
1848,
1893,
1896,
1897,
1910,
1965,
2020,
2021,
2033,
2061,
2084,
2085,
2102,
2129,
2171,
2248,
2251,
2252,
2276,
2316,
2356,
2381,
2443,
2511,
2537,
2729,
2783,
2817,
2889,
2961,
2975,
3005,
3067,
3077,
3078,
3103,
3179,
3211,
3257,
3271,
3290,
3440,
3633,
3658,
3722,
3750,
3764,
3811,
3821,
3862,
3897,
3951,
3965,
4027,
4089,
4138,
4170,
4216,
4250,
4260,
4267,
4271,
4281,
4313,
4327,
4350,
4373,
4410,
4494,
4525,
4574,
4612,
4680,
4691,
4692,
4750,
4789,
4841,
4902,
4903,
4977,
4996,
5014,
5035,
5102,
5155,
5156,
5180,
5224,
5287,
5312,
5326,
5394,
5419,
5433,
5452,
5477,
5491,
5501,
5516,
5547,
5568,
5578,
5579,
5608,
5609,
5621,
5646,
5690,
5739,
5886,
5887,
5926,
5983,
5993,
6008,
6057,
6095,
6134,
6144,
6154,
6155,
6177,
6187,
6188,
6229,
6237,
6238,
6247,
6255,
6256,
6263,
6289,
6334,
6365,
6395,
6448,
6463,
6507,
6556,
6612,
6893,
6912,
6927,
6957,
7010,
7070,
7112,
7225,
7244,
7259,
7292,
7373,
7390,
7420,
7474,
7529,
7530,
7549,
7591,
7625,
7669,
7809,
7843,
7870,
7915,
7961,
8215,
8297,
8398,
8429,
8477,
8588,
8760,
8791,
8818,
8841,
8875,
8919,
9058,
9092,
9119,
9164,
9210,
9468,
9552,
9654,
9685,
9733,
9846,
10020,
10051,
10078,
10101,
10120,
10135,
10230,
10267,
10366,
10381,
10392,
10428,
10446,
10459,
10478,
10479,
10513,
10575,
10641,
10709,
10781,
10826,
10872,
10920,
10980,
11034,
11098,
11156,
11166,
11167,
11229,
11271,
11315,
11325,
11326,
11327,
11334,
11335,
11374,
11438,
11492,
11559,
11622,
11680,
11681,
11732,
11783,
11824,
11852,
11881,
11939,
11987,
11994,
11995,
11996,
12037,
12107,
12152,
12206,
12232,
12242,
12263,
12270,
12278,
12310,
12338,
12346,
12388,
12450,
12516,
12610,
12710,
12735,
12745,
12779,
12801,
12808,
12816,
12843,
12868,
12876,
12913,
12973,
12998,
13077,
13160,
13243,
13336,
13421,
13510,
13583,
13619,
13655,
13695,
13736,
13774,
13775,
13837,
13903,
13961,
14023,
14024,
14047,
14054,
14062,
14092,
14121,
14129,
14169,
14303,
14349,
14350,
14399,
14442,
14456,
14475,
14545,
14618,
14705,
14706,
14785,
14878,
14879,
14934,
14962,
14986,
15004,
15027,
15134,
15221,
15222,
15335,
15428,
15429,
15484,
15512,
15536,
15554,
15555,
15569,
15579,
15586,
15630,
15671,
15672,
15711,
15743,
15786,
15796,
15797,
15837,
15898,
15899,
15923,
15961,
15999,
16081,
16165,
16210,
16246,
16293,
16367,
16393,
16417,
16461,
16479,
16502,
16608,
16643,
16667,
16711,
16729,
16743,
16762,
16803,
16834,
16854,
16894,
16908,
16919,
16947,
16954,
17116,
17169,
17208,
17252,
17253,
17293,
17355,
17356,
17380,
17418,
17456,
17538,
17629,
17686,
17704,
17727,
17777,
17816,
17860,
17878,
17892,
17911,
17954,
17989,
18029,
18043,
18054,
18082,
18089,
18090,
18142,
18212,
18251,
18306,
18307,
18347,
18415,
18416,
18440,
18478,
18516,
18598,
18689,
18746,
18764,
18787,
18837,
18876,
18920,
18938,
18952,
18971,
19014,
19049,
19089,
19103,
19114,
19142,
19149,
19150,
19197,
19261,
19323,
19362,
19421,
19428,
19429,
19437,
19465,
19494,
19502,
19544,
19595,
19658,
19668,
19683,
19714,
19752,
19795,
19835,
19878,
19879,
19951,
19996,
19997,
20067,
20119,
20167,
20168,
20224,
20273,
20317,
20361,
20409,
20410,
20461,
20462,
20477,
20487,
20494,
20522,
20563,
20627,
20662,
20706,
20746,
20768,
20769,
20830,
20915,
21035,
21045,
21052,
21090,
21252,
21253,
21284,
21304,
21324,
21334,
21348,
21403,
21438,
21499,
21547,
21639,
21679,
21680,
21759,
21813,
21814,
21838,
21852,
21885,
21895,
21915,
21943,
21953,
21959,
21979,
22016,
22041,
22070,
22112,
22290,
22334,
22512,
22518,
22519,
22527,
22552,
22560,
22601,
22687,
22705,
22729,
22751,
22774,
22792,
22807,
22841,
22842,
22875,
22904,
22960,
22984,
23017,
23081,
23095,
23143,
23206,
23246,
23274,
23330,
23344,
23354,
23355,
23372,
23401,
23428,
23439,
23446,
23454,
23474,
23482,
23520,
23533,
23576,
23600,
23627,
23655,
23683,
23701,
23747,
23771,
23800,
23838,
23873,
23891,
23983,
24041,
24087,
24142,
24155,
24167,
24168,
24253,
24333,
24375,
24452,
24491,
24549,
24563,
24607,
24669,
24768,
24801,
24819,
24842,
24876,
24894,
24908,
24927,
24957,
24971,
24981,
24994,
25029,
25066,
25087,
25099,
25157,
25196,
25249,
25311,
25325,
25368,
25422,
25436,
25494,
25557,
25586,
25600,
25619,
25649,
25663,
25673,
25674,
25687,
25722,
25760,
25781,
25793,
25848,
25898,
25950,
26000,
26084,
26130,
26284,
26314,
26328,
26347,
26376,
26390,
26400,
26413,
26448,
26488,
26509,
26521,
26576,
26625,
26676,
26726,
26810,
26863,
27013,
27043,
27057,
27076,
27105,
27119,
27129,
27130,
27131,
27132,
27167,
27219,
27249,
27263,
27282,
27329,
27363,
27381,
27404,
27437,
27455,
27469,
27480,
27490,
27504,
27514,
27527,
27545,
27546,
27582,
27631,
27682,
27744,
27778,
27779,
27820,
27885,
27927,
27928,
27971,
28032,
28033,
28060,
28103,
28160,
28191,
28192,
28193,
28219,
28264,
28379,
28389,
28420,
28466,
28593,
28603,
28634,
28680,
28796,
28806,
28837,
28881,
28985,
28995,
28996,
29037,
29038,
29112,
29113,
29119,
29133,
29161,
29162,
29170,
29171
],
"line_end_idx": [
5,
6,
36,
37,
59,
60,
90,
91,
121,
122,
136,
137,
191,
227,
259,
260,
300,
333,
361,
389,
421,
422,
437,
438,
492,
520,
521,
526,
527,
543,
550,
551,
558,
583,
608,
694,
750,
798,
843,
875,
889,
942,
943,
973,
985,
1001,
1068,
1074,
1088,
1156,
1214,
1246,
1256,
1272,
1278,
1290,
1351,
1400,
1435,
1436,
1457,
1503,
1608,
1664,
1848,
1893,
1896,
1897,
1910,
1965,
2020,
2021,
2033,
2061,
2084,
2085,
2102,
2129,
2171,
2248,
2251,
2252,
2276,
2316,
2356,
2381,
2443,
2511,
2537,
2729,
2783,
2817,
2889,
2961,
2975,
3005,
3067,
3077,
3078,
3103,
3179,
3211,
3257,
3271,
3290,
3440,
3633,
3658,
3722,
3750,
3764,
3811,
3821,
3862,
3897,
3951,
3965,
4027,
4089,
4138,
4170,
4216,
4250,
4260,
4267,
4271,
4281,
4313,
4327,
4350,
4373,
4410,
4494,
4525,
4574,
4612,
4680,
4691,
4692,
4750,
4789,
4841,
4902,
4903,
4977,
4996,
5014,
5035,
5102,
5155,
5156,
5180,
5224,
5287,
5312,
5326,
5394,
5419,
5433,
5452,
5477,
5491,
5501,
5516,
5547,
5568,
5578,
5579,
5608,
5609,
5621,
5646,
5690,
5739,
5886,
5887,
5926,
5983,
5993,
6008,
6057,
6095,
6134,
6144,
6154,
6155,
6177,
6187,
6188,
6229,
6237,
6238,
6247,
6255,
6256,
6263,
6289,
6334,
6365,
6395,
6448,
6463,
6507,
6556,
6612,
6893,
6912,
6927,
6957,
7010,
7070,
7112,
7225,
7244,
7259,
7292,
7373,
7390,
7420,
7474,
7529,
7530,
7549,
7591,
7625,
7669,
7809,
7843,
7870,
7915,
7961,
8215,
8297,
8398,
8429,
8477,
8588,
8760,
8791,
8818,
8841,
8875,
8919,
9058,
9092,
9119,
9164,
9210,
9468,
9552,
9654,
9685,
9733,
9846,
10020,
10051,
10078,
10101,
10120,
10135,
10230,
10267,
10366,
10381,
10392,
10428,
10446,
10459,
10478,
10479,
10513,
10575,
10641,
10709,
10781,
10826,
10872,
10920,
10980,
11034,
11098,
11156,
11166,
11167,
11229,
11271,
11315,
11325,
11326,
11327,
11334,
11335,
11374,
11438,
11492,
11559,
11622,
11680,
11681,
11732,
11783,
11824,
11852,
11881,
11939,
11987,
11994,
11995,
11996,
12037,
12107,
12152,
12206,
12232,
12242,
12263,
12270,
12278,
12310,
12338,
12346,
12388,
12450,
12516,
12610,
12710,
12735,
12745,
12779,
12801,
12808,
12816,
12843,
12868,
12876,
12913,
12973,
12998,
13077,
13160,
13243,
13336,
13421,
13510,
13583,
13619,
13655,
13695,
13736,
13774,
13775,
13837,
13903,
13961,
14023,
14024,
14047,
14054,
14062,
14092,
14121,
14129,
14169,
14303,
14349,
14350,
14399,
14442,
14456,
14475,
14545,
14618,
14705,
14706,
14785,
14878,
14879,
14934,
14962,
14986,
15004,
15027,
15134,
15221,
15222,
15335,
15428,
15429,
15484,
15512,
15536,
15554,
15555,
15569,
15579,
15586,
15630,
15671,
15672,
15711,
15743,
15786,
15796,
15797,
15837,
15898,
15899,
15923,
15961,
15999,
16081,
16165,
16210,
16246,
16293,
16367,
16393,
16417,
16461,
16479,
16502,
16608,
16643,
16667,
16711,
16729,
16743,
16762,
16803,
16834,
16854,
16894,
16908,
16919,
16947,
16954,
17116,
17169,
17208,
17252,
17253,
17293,
17355,
17356,
17380,
17418,
17456,
17538,
17629,
17686,
17704,
17727,
17777,
17816,
17860,
17878,
17892,
17911,
17954,
17989,
18029,
18043,
18054,
18082,
18089,
18090,
18142,
18212,
18251,
18306,
18307,
18347,
18415,
18416,
18440,
18478,
18516,
18598,
18689,
18746,
18764,
18787,
18837,
18876,
18920,
18938,
18952,
18971,
19014,
19049,
19089,
19103,
19114,
19142,
19149,
19150,
19197,
19261,
19323,
19362,
19421,
19428,
19429,
19437,
19465,
19494,
19502,
19544,
19595,
19658,
19668,
19683,
19714,
19752,
19795,
19835,
19878,
19879,
19951,
19996,
19997,
20067,
20119,
20167,
20168,
20224,
20273,
20317,
20361,
20409,
20410,
20461,
20462,
20477,
20487,
20494,
20522,
20563,
20627,
20662,
20706,
20746,
20768,
20769,
20830,
20915,
21035,
21045,
21052,
21090,
21252,
21253,
21284,
21304,
21324,
21334,
21348,
21403,
21438,
21499,
21547,
21639,
21679,
21680,
21759,
21813,
21814,
21838,
21852,
21885,
21895,
21915,
21943,
21953,
21959,
21979,
22016,
22041,
22070,
22112,
22290,
22334,
22512,
22518,
22519,
22527,
22552,
22560,
22601,
22687,
22705,
22729,
22751,
22774,
22792,
22807,
22841,
22842,
22875,
22904,
22960,
22984,
23017,
23081,
23095,
23143,
23206,
23246,
23274,
23330,
23344,
23354,
23355,
23372,
23401,
23428,
23439,
23446,
23454,
23474,
23482,
23520,
23533,
23576,
23600,
23627,
23655,
23683,
23701,
23747,
23771,
23800,
23838,
23873,
23891,
23983,
24041,
24087,
24142,
24155,
24167,
24168,
24253,
24333,
24375,
24452,
24491,
24549,
24563,
24607,
24669,
24768,
24801,
24819,
24842,
24876,
24894,
24908,
24927,
24957,
24971,
24981,
24994,
25029,
25066,
25087,
25099,
25157,
25196,
25249,
25311,
25325,
25368,
25422,
25436,
25494,
25557,
25586,
25600,
25619,
25649,
25663,
25673,
25674,
25687,
25722,
25760,
25781,
25793,
25848,
25898,
25950,
26000,
26084,
26130,
26284,
26314,
26328,
26347,
26376,
26390,
26400,
26413,
26448,
26488,
26509,
26521,
26576,
26625,
26676,
26726,
26810,
26863,
27013,
27043,
27057,
27076,
27105,
27119,
27129,
27130,
27131,
27132,
27167,
27219,
27249,
27263,
27282,
27329,
27363,
27381,
27404,
27437,
27455,
27469,
27480,
27490,
27504,
27514,
27527,
27545,
27546,
27582,
27631,
27682,
27744,
27778,
27779,
27820,
27885,
27927,
27928,
27971,
28032,
28033,
28060,
28103,
28160,
28191,
28192,
28193,
28219,
28264,
28379,
28389,
28420,
28466,
28593,
28603,
28634,
28680,
28796,
28806,
28837,
28881,
28985,
28995,
28996,
29037,
29038,
29112,
29113,
29119,
29133,
29161,
29162,
29170,
29171,
29178
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 29178,
"ccnet_original_nlines": 788,
"rps_doc_curly_bracket": 0.009116459637880325,
"rps_doc_ldnoobw_words": 3,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.036496348679065704,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.005109489895403385,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.5888686180114746,
"rps_doc_frac_unique_words": 0.43603482842445374,
"rps_doc_mean_word_length": 10.224380493164062,
"rps_doc_num_sentences": 528,
"rps_doc_symbol_to_word_ratio": 0.0009124099742621183,
"rps_doc_unigram_entropy": 5.760591506958008,
"rps_doc_word_count": 1493,
"rps_doc_frac_chars_dupe_10grams": 0.08915820717811584,
"rps_doc_frac_chars_dupe_5grams": 0.21493613719940186,
"rps_doc_frac_chars_dupe_6grams": 0.16842450201511383,
"rps_doc_frac_chars_dupe_7grams": 0.1486406773328781,
"rps_doc_frac_chars_dupe_8grams": 0.11601702868938446,
"rps_doc_frac_chars_dupe_9grams": 0.08915820717811584,
"rps_doc_frac_chars_top_2gram": 0.007468060124665499,
"rps_doc_frac_chars_top_3gram": 0.004127089865505695,
"rps_doc_frac_chars_top_4gram": 0.010481489822268486,
"rps_doc_books_importance": -2136.69189453125,
"rps_doc_books_importance_length_correction": -2136.69189453125,
"rps_doc_openwebtext_importance": -1013.4857177734375,
"rps_doc_openwebtext_importance_length_correction": -1013.4857177734375,
"rps_doc_wikipedia_importance": -900.4793701171875,
"rps_doc_wikipedia_importance_length_correction": -900.4793701171875
},
"fasttext": {
"dclm": 0.9997560381889343,
"english": 0.11032695323228836,
"fineweb_edu_approx": 3.597296714782715,
"eai_general_math": 0.38713401556015015,
"eai_open_web_math": 0.11059021949768066,
"eai_web_code": 0.9656354188919067
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "-1",
"labels": {
"level_1": "",
"level_2": "",
"level_3": ""
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v1": {
"primary": {
"code": "4",
"label": "Code/Software"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "1",
"label": "Leftover HTML"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "23",
"label": "Tutorial"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "4",
"label": "Graduate/Expert Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-81,712,823,336,784,590
|
Generic Routing Encapsulation (GRE) is a tunneling protocol, developed by Cisco.
learn more… | top users | synonyms
4
votes
1answer
10k views
PPTP connection fails with errors 800/806
I've got a client (Server 2008 R2) that won't connect to our production environment PPTP VPN server (Server 2003, running RRAS). The server is behind a firewall that has TCP1723 open as well as GRE. ...
2
votes
1answer
609 views
Redirect SSH traffic through GRE tunnel
I'm trying to redirect all local connections with destination matchs port 22 to specified tunnel using iptables MARK, but, something is going wrong. 1.1.1.1 my public address 2.2.2.2 tunnel public ...
2
votes
1answer
3k views
How to force certain traffic through GRE tunnel?
Here's what I do. Server (public internet is 222.x.x.x): echo 'net.ipv4.ip_forward=1' >> /etc/sysctl.conf sysctl -p iptunnel add gre1 mode gre local 222.x.x.x remote 115.x.x.x ttl 255 ...
1
vote
1answer
402 views
Using my IPs on OVH server via GRE
I can't route my IPs into a OVH server, can you help me to find the problem? Mikrotik GRE IP: 192.168.55.10 OVH Server GRE IP: 192.168.55.20 GRE iface name: ali1_fr1-ovz1 IP to route from Mikrotik to ...
1
vote
1answer
755 views
Ubuntu GRE local ip address, wan ip of router, or ip of ubuntu server
I have an ubuntu server behind a router that I am configuring to have a GRE tunnel to another remote device across the interwebs. in the config, I add the line: pre-up iptunnel add tun1 mode gre ...
1
vote
1answer
874 views
How to enable debug logging for GRE?
How to enable debug logging for module ip_gre on linux 2.6?
0
votes
1answer
23 views
GRE protocol type for Ethernet over GRE?
For a IP over GRE tunnel, as defined by the RFC 2784, the "protocol" field is filled with 0x0800 (defined as ETH_P_IP in the Linux kernel according to this source http://www.scs.stanford.edu/histar/...
0
votes
1answer
71 views
Reverse proxy for DoS / DDoS protection
after i search how to protect my website host server using GRE tunnels, some friends of this forum give me a tip to use Reverse Proxy that would be better. But i don't found any guide on how to ...
0
votes
1answer
151 views
Load balancing between two (or more) GRE tunnels
I have a hosted service (think zScaler™) that is having me send my traffic to it via GRE tunnels. I am given two appliances and want to load balance my traffic between the two tunnels. I could ...
0
votes
1answer
134 views
Amazon Linux - iptables NAT rules not matching GRE traffic
I'm trying to prototype something in AWS VPC/EC2, but I can't get my NAT rules to work. I have the following setup (all instances running the Amazon Linux AMI): GRE Tunnel between instances 10.0.0....
0
votes
1answer
136 views
Set up transparent GRE/VPN to redirect all traffic to an External datacenter
I need to setup an existing server with multiple IPs (from OVH) to send all the traffic (through VPN or GRE tunnel) to an external server that has only 1 Public IP. I want to make it like every local ...
0
votes
1answer
482 views
TLS-intolerant sites suddenly not working
About 2 weeks ago users started reporting that they were unable to access two https-only sites. When I inspected these sites I found they were completely intolerant to TLS. In order to connect, SSL3 ...
0
votes
1answer
575 views
GRE Tunnel in CentOS
How to create a GRE Tunnel in CentOS pointing all connections to server A for the server B? I have a public server with DDoS protection and need to use this as a firewall to filter acess to the other ...
0
votes
1answer
716 views
How to troubleshoot GRE tunnel issues?
I commonly run into issues where a GRE tunnel (CentOS server to server, not router based) works and pings fine from both ends but the IP / Range being tunneled does not function. This almost always ...
0
votes
1answer
2k views
Gre Tunnel Cisco Linux traffic forwarding
I setup a gre tunnel a cisco router and a Linux machine, the tunnel interface in the Linux box named pic. Well i have to forward traffic coming from cisco through the Linux box. the rules i've set in ...
1
vote
0answers
36 views
What could cause racoonctl to show a Phase2 count higher than the number of ports racoon is listening on?
In my setup I have some EC2 instances in different regions linked by GRE tunnels, using ISAKMP via racoon. This setup is inherited, so bear with me if I fumble with terminology. Sometimes I get weird ...
1
vote
0answers
121 views
Ethernet over GRE bridging - Proxmox
I'm trying to install two proxmox on Online.net server's, and I just realized that their RPN feature doesn't work at all like the OVH vRacks. Since I need the different VM's on both hypervisors to be ...
1
vote
0answers
41 views
Cisco 1941 EIGRP UP DOWN
We have two cisco routers 1841 and 1941. The 1841 keeps generating "holding time expired" and "interface goodbye recieved" about its neighbor the 1941. The VPN IPSec protocol seems to stay up. ...
1
vote
0answers
54 views
internet access for system over multiple hops of ipsec using GRE and OSPF
I have the following setup: linux client @ 172.16.10.68 linux gateway @ 172.16.10.69, ipsec tunnel to aws box #1, gre tunnel 10.254.0.0/30 aws box #1, ipsec tunnel from linux gw, ipsec tunnel to ...
1
vote
0answers
44 views
IP Tables forwarding tun0 over gre1 (OpenVPN)
I haven't found a very descriptive thread (and sorry if there is one in existence - in my several hours of searching I've found nothing to my specific situation). My main issue here is getting my ...
1
vote
0answers
1k views
OpenNHRP configuration without IPsec
I'm attempting to use OpenNHRP on a linux box to connect with a Cisco Router. I want to allow GRE tunnels from the linux box to the Cisco router dynamically, but I'm not implementing DMVPN on the ...
1
vote
0answers
456 views
GRE debug: “adding 0 encap bytes”?
What this debug message actually means? Shouldn't encapsulation add 24 extra bytes or not? For what reason encapsulation is not adding bytes to original packet in this debug message? Dec 28 23:45:39....
0
votes
0answers
5 views
Changing the gretap tunnel destination address droping the dhcp offer packets
I am having problem setup the L2 over GRE tunnel. create and enable the GRE tunnel: ip link add gre0 type gretap remote (WAG1 IP) local (local ip) ifconfig gre0 up its working fine. Now i ...
0
votes
0answers
13 views
Building a meshed overlay network with outgoing connections going through a gateway
I rent a few Linux servers and the provider doesn't offer a VLAN. Each server gets a public IPv4 address, which are not part of the same subnet. I would like to create a network which "hides" the ...
0
votes
0answers
28 views
multi gre tunnels to one IP
I have an issue with GRE tunnels after connecting multi-GRE tunnels with different IP's to the server, using this tutorial: http://wiki.buyvm.net/doku.php/gre_tunnel every GRE tunnel has interface ...
0
votes
0answers
22 views
DNS using GRE work 50%
l'm in a big issue here to make it work I'm already at least about 60% done, but it is difficult and I would like to count on the help guys here who may have already done this type of configuration. ...
0
votes
0answers
119 views
TCP Out-of-order packets over GRE causing disconnect
I'm experiencing an issue with a small percentage of TCP connections over a GRE tunnel between two servers. The topology is basically Internet <-> GRE Tunnel <-> Backend The GRE tunnel and the ...
0
votes
0answers
377 views
Strongswan IPsec: routing arbitrary subnets over /32 IPsec endpoints
I have a basic setup between two sites A (FreeBSD, 10.0.0.1/24 nat'd to 1.1.1.1), B (Linux, 2.2.2.2), with only A behind NAT. I've only been able to get it working in tunnel mode. Here's my ipsec.conf:...
0
votes
0answers
77 views
Openbsd set connect on PPTP server behind packet filter
I have firewall on OpenBSD use Packet Filter and behind him MS Windows server with PPTP server. I need allow connect this PPTP server from internet. I set in OpenBSD: net.inet.gre.allow=1 net.inet....
0
votes
0answers
75 views
GRE Tunnel Collapsing in One Direction
This is a related question to another thread I posted. I'm having an issue where my GRE tunnel is collapsing in one direction, but can be reopened by ping the other server using the GRE Interface. I'...
0
votes
0answers
128 views
Listening “through” GRE Tunnel
Currently I'm looking to learn about using GRE Tunnels and I have the following scheme: Server1 (200.1.2.3) ----> Server2 (190.1.2.3) Both servers have public IPs Then I've setup a GRE Tunnel with ...
0
votes
0answers
328 views
Using public interfaces on a server connected through a GRE tunnel
I'm pretty new to networking so please forgive any terminology mistakes. I have 2 servers connected with a GRE tunnel. Server1 (10.0.0.1) ----> Server2 (10.0.0.2) I want to be able to bind to the ...
|
{
"url": "http://serverfault.com/questions/tagged/gre?sort=unanswered&pagesize=15",
"source_domain": "serverfault.com",
"snapshot_id": "crawl=CC-MAIN-2016-30",
"warc_metadata": {
"Content-Length": "133722",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:JLWCX4U6CZMVRP47KIKBFD34INXFV2IC",
"WARC-Concurrent-To": "<urn:uuid:878f953d-c4e4-4301-a874-460d9000db78>",
"WARC-Date": "2016-07-24T11:09:25Z",
"WARC-IP-Address": "151.101.129.69",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:PSXMOJENODOFECMLOF6T6S2BN7PUKOY7",
"WARC-Record-ID": "<urn:uuid:552c7e82-d481-4eb4-9779-df6b057c49f1>",
"WARC-Target-URI": "http://serverfault.com/questions/tagged/gre?sort=unanswered&pagesize=15",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:30eee7b4-48eb-4e76-b7e2-583d9cde620b>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-185-27-174.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2016-30\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web for July 2016\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
81,
82,
117,
118,
120,
126,
134,
144,
145,
187,
188,
391,
393,
399,
407,
417,
418,
458,
459,
660,
662,
668,
676,
685,
686,
735,
736,
924,
926,
931,
939,
949,
950,
985,
986,
1190,
1192,
1197,
1205,
1215,
1216,
1286,
1287,
1486,
1488,
1493,
1501,
1511,
1512,
1549,
1550,
1610,
1612,
1618,
1626,
1635,
1636,
1677,
1678,
1880,
1882,
1888,
1896,
1905,
1906,
1946,
1947,
2145,
2147,
2153,
2161,
2171,
2172,
2221,
2222,
2419,
2421,
2427,
2435,
2445,
2446,
2505,
2506,
2707,
2709,
2715,
2723,
2733,
2734,
2811,
2812,
3016,
3018,
3024,
3032,
3042,
3043,
3085,
3086,
3289,
3291,
3297,
3305,
3315,
3316,
3337,
3338,
3542,
3544,
3550,
3558,
3568,
3569,
3608,
3609,
3811,
3813,
3819,
3827,
3836,
3837,
3879,
3880,
4084,
4086,
4091,
4100,
4109,
4110,
4216,
4217,
4421,
4423,
4428,
4437,
4447,
4448,
4485,
4486,
4690,
4692,
4697,
4706,
4715,
4716,
4741,
4742,
4939,
4941,
4946,
4955,
4964,
4965,
5039,
5040,
5239,
5241,
5246,
5255,
5264,
5265,
5311,
5312,
5512,
5514,
5519,
5528,
5537,
5538,
5575,
5576,
5776,
5778,
5783,
5792,
5802,
5803,
5838,
5839,
6042,
6044,
6050,
6059,
6067,
6068,
6146,
6147,
6339,
6341,
6347,
6356,
6365,
6366,
6450,
6451,
6651,
6653,
6659,
6668,
6677,
6678,
6706,
6707,
6908,
6910,
6916,
6925,
6934,
6935,
6958,
6959,
7162,
7164,
7170,
7179,
7189,
7190,
7243,
7244,
7441,
7443,
7449,
7458,
7468,
7469,
7538,
7539,
7744,
7746,
7752,
7761,
7770,
7771,
7827,
7828,
8029,
8031,
8037,
8046,
8055,
8056,
8095,
8096,
8299,
8301,
8307,
8316,
8326,
8327,
8358,
8359,
8560,
8562,
8568,
8577,
8587,
8588,
8655,
8656
],
"line_end_idx": [
81,
82,
117,
118,
120,
126,
134,
144,
145,
187,
188,
391,
393,
399,
407,
417,
418,
458,
459,
660,
662,
668,
676,
685,
686,
735,
736,
924,
926,
931,
939,
949,
950,
985,
986,
1190,
1192,
1197,
1205,
1215,
1216,
1286,
1287,
1486,
1488,
1493,
1501,
1511,
1512,
1549,
1550,
1610,
1612,
1618,
1626,
1635,
1636,
1677,
1678,
1880,
1882,
1888,
1896,
1905,
1906,
1946,
1947,
2145,
2147,
2153,
2161,
2171,
2172,
2221,
2222,
2419,
2421,
2427,
2435,
2445,
2446,
2505,
2506,
2707,
2709,
2715,
2723,
2733,
2734,
2811,
2812,
3016,
3018,
3024,
3032,
3042,
3043,
3085,
3086,
3289,
3291,
3297,
3305,
3315,
3316,
3337,
3338,
3542,
3544,
3550,
3558,
3568,
3569,
3608,
3609,
3811,
3813,
3819,
3827,
3836,
3837,
3879,
3880,
4084,
4086,
4091,
4100,
4109,
4110,
4216,
4217,
4421,
4423,
4428,
4437,
4447,
4448,
4485,
4486,
4690,
4692,
4697,
4706,
4715,
4716,
4741,
4742,
4939,
4941,
4946,
4955,
4964,
4965,
5039,
5040,
5239,
5241,
5246,
5255,
5264,
5265,
5311,
5312,
5512,
5514,
5519,
5528,
5537,
5538,
5575,
5576,
5776,
5778,
5783,
5792,
5802,
5803,
5838,
5839,
6042,
6044,
6050,
6059,
6067,
6068,
6146,
6147,
6339,
6341,
6347,
6356,
6365,
6366,
6450,
6451,
6651,
6653,
6659,
6668,
6677,
6678,
6706,
6707,
6908,
6910,
6916,
6925,
6934,
6935,
6958,
6959,
7162,
7164,
7170,
7179,
7189,
7190,
7243,
7244,
7441,
7443,
7449,
7458,
7468,
7469,
7538,
7539,
7744,
7746,
7752,
7761,
7770,
7771,
7827,
7828,
8029,
8031,
8037,
8046,
8055,
8056,
8095,
8096,
8299,
8301,
8307,
8316,
8326,
8327,
8358,
8359,
8560,
8562,
8568,
8577,
8587,
8588,
8655,
8656,
8855
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 8855,
"ccnet_original_nlines": 259,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.29738059639930725,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.08371853828430176,
"rps_doc_frac_lines_end_with_ellipsis": 0.11923076957464218,
"rps_doc_frac_no_alph_words": 0.24139702320098877,
"rps_doc_frac_unique_words": 0.3549668788909912,
"rps_doc_mean_word_length": 4.524503231048584,
"rps_doc_num_sentences": 147,
"rps_doc_symbol_to_word_ratio": 0.01746276021003723,
"rps_doc_unigram_entropy": 5.512963771820068,
"rps_doc_word_count": 1510,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.014051520265638828,
"rps_doc_frac_chars_dupe_6grams": 0.007611239794641733,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.03293326124548912,
"rps_doc_frac_chars_top_3gram": 0.02049179933965206,
"rps_doc_frac_chars_top_4gram": 0.007464869879186153,
"rps_doc_books_importance": -853.7968139648438,
"rps_doc_books_importance_length_correction": -853.7968139648438,
"rps_doc_openwebtext_importance": -578.4798583984375,
"rps_doc_openwebtext_importance_length_correction": -578.4798583984375,
"rps_doc_wikipedia_importance": -357.716064453125,
"rps_doc_wikipedia_importance_length_correction": -357.716064453125
},
"fasttext": {
"dclm": 0.02872180938720703,
"english": 0.9055495262145996,
"fineweb_edu_approx": 1.2960574626922607,
"eai_general_math": 0.0026690401136875153,
"eai_open_web_math": 0.11902589350938797,
"eai_web_code": 0.001091000041924417
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.6",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "005.457",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "4",
"label": "Analyze"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "4",
"label": "Graduate/Expert Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-6,673,340,888,929,802,000
|
Inquiry CartInquiry Cart
Home - blog
What Is Poe Switch: Everything You Need to Know
August 7, 2023
Contents hide
What is a Poe Switch and How Does It Work?
Want to simplify your network cabling and reduce costs? Look no further than Power over Ethernet (PoE) switches. These innovative switches transmit data and power through a single Ethernet cable, eliminating the need for separate power cords.
What are PoE Switches, and How Do They Work?
A PoE switch is a network switch that can seamlessly deliver power and data through one Ethernet cable. This means you can power PoE-enabled devices like IP cameras, wireless access points, and VoIP phones without the hassle of extra wires. PoE switches adhere to the IEEE 802.3af and 802.3at standards, providing up to 30W of power per port.
PoE switches detect the power needs of connected devices and supply the necessary power. They achieve this by injecting a small amount of energy into the Ethernet signal, which is then received by the device’s built-in PoE receiver. The device extracts the punch and utilizes it to function.
Benefits of PoE Switches
Here are some of the advantages of using PoE switches:
Simplified network cabling: Say goodbye to tangled cables and reduce clutter by eliminating the need for separate power cords.
Cost savings: Save on purchasing and installing separate power cables and outlets.
Flexibility: Place powered devices in remote areas where power sources may be scarce or challenging to access.
Enhanced safety: PoE switches prioritize safety by ensuring correct power delivery, mitigating the risk of electrical shocks.
PoE switch
Main Types of PoE Switches
There are three primary types of PoE switches to choose from:
End-span PoE switches: The same Ethernet cable delivers power and data simultaneously.
Mid-span PoE switch: Power is supplied through a separate Ethernet cable, making it an ideal choice for existing network installations.
Complete PoE+ switch: This high-powered switch is perfect for devices with significant power requirements, such as PTZ IP cameras.
Using PoE Switches in Your Network
To implement PoE switches in your network, follow these simple steps:
Verify compatibility: Ensure that your devices support PoE functionality.
Connect the button: Use a standard Ethernet cable to connect the PoE switch to your existing network.
Connect devices: Attach your PoE-enabled devices to the PoE switch.
Power on: Activate the PoE switch to detect connected devices and power them automatically.
Tips for Powering Devices with PoE Switches
When using PoE switches to power your devices, keep these considerations in mind:
Use the correct cable: Select the appropriate line to prevent power loss or damage to connected devices.
Check power requirements: Ensure that the total power requirements of your devices do not exceed the switch’s power budget.
Compatibility is critical: Make sure your PoE-enabled devices are compatible with the specific PoE switch you intend to use.
Understanding Power Budget in PoE Switches
The power budget of a PoE switch represents the total amount of power it can supply across all its ports. Considering the power budget when connecting devices to a PoE switch is crucial. Exceeding the power budget can lead to a shutdown, interrupting the power supply to connected devices.
Upgrade your network with PoE switches for a streamlined, cost-effective solution to power your devices.
Recommended Reading: Data Center Network Architecture
Why Should You Use Poe Switches?
Poe Switches, or Power over Ethernet switches, have transformed the networking industry by enabling data and power delivery over a single Ethernet cable. This groundbreaking technology allows network administrators to power IP devices like wireless access points, IP cameras, and VoIP phones through a Poe switch, eliminating the need for extra power sources and simplifying installation and maintenance processes.
Advantages of Poe Switches
There are several advantages to using Poe switches instead of traditional powered devices. Firstly, Poe switches offer flexibility and scalability, making it easy to expand networks, even in challenging locations where conventional power sources are unavailable.
Secondly, Poe switches offer cost savings by powering devices through a single Ethernet cable. This eliminates the need for extra power cables, outlets, and surge protectors, resulting in significant cost savings. Moreover, Poe switches reduce overall power consumption by controlling device power supply, minimizing wasted power.
Furthermore, Poe switches are ideal for network security. They provide a reliable power supply to critical devices, ensuring uninterrupted operation during power outages. This is particularly important for institutions like hospitals and schools that rely heavily on network connectivity for essential functions.
Poe Switch Applications in Various Scenarios
Poe switches are beneficial in various network scenarios, from small offices to large-scale enterprises. In office buildings, Poe switches are perfect for powering multiple devices like wireless access points, IP phones, and surveillance cameras. They streamline connectivity by eliminating the need for additional power sources, making network management more efficient while reducing installation and maintenance costs.
In healthcare facilities, Poe switches simplify the installation and maintenance of medical devices such as monitoring systems, infusion pumps, and ventilators. This allows medical professionals to focus on patient care. Similarly, Poe switches are ideal for schools and universities, where PoE technology powers projectors, interactive whiteboards, and security cameras, greatly enhancing the learning experience.
Using Poe Switches for Wireless Access Points
Poe switches simplify the installation of wireless access points by providing network connectivity and power through a single cable. This eliminates the need for extra power sources, which is particularly advantageous in large establishments like shopping malls and airports that require multiple access points for uninterrupted wireless connectivity.
Simplifying the Installation of IP Cameras with Poe Switches
Poe switches are an excellent choice for IP camera installations due to their minimal cabling requirements and remote powering capabilities. By removing the need for bulky power outlets and reducing overall cabling, Poe switches make the installation process less invasive, lower maintenance costs, and improve network performance.
Powering VoIP Phones with Poe Switches
Poe switches simplify the installation and management of VoIP phones by powering them through a single Ethernet cable, ensuring reliable and uninterrupted connectivity. This cost-effective solution eliminates the need for extra power sources, reduces cabling requirements, and simplifies installation.
Recommended Reading: Everything You Need to Know about SFP Ports
How to Choose the Right Poe Switch
Cisco_SG_200-08P_front
Simplify Your PoE Switch Selection Process: A Comprehensive Guide
Power over Ethernet (PoE) switches are known for their convenience and cost-effectiveness, making them a popular choice for businesses. But, selecting the right PoE switch can be overwhelming, especially if you’re not tech-savvy. In this article, we’ll take you through the process, explaining the differences between managed and unmanaged switches, essential factors to consider, understanding PoE power budget and power per port, and key features to look for.
Managed Vs. Unmanaged PoE Switches: What You Need to Know
Managed switches offer advanced control and configuration options like VLANs and Quality of Service (QoS), improving network efficiency. Unmanaged switches are plug-and-play devices with minimal configuration, providing essential connectivity. If your business requires advanced network management, choose a managed PoE switch. An unmanaged PoE switch will do the job for simple and straightforward needs.
Essential Factors to Consider When Selecting a PoE Switch
Keep these factors in mind when choosing your PoE switch:
PoE Standards: Check if your devices are compatible with the standards supported by the controller (e.g., IEEE 802.3af, IEEE 802.3at).
Port Density: Determine the number of devices you want to connect and choose a switch with the correct number of ports.
Power Budget: Consider the power requirements of your devices and ensure the switch’s power budget can meet them.
Switch Type: Decide between a rack-mounted or desktop switch based on your business’s network size and layout.
Understanding PoE Power Budget for Efficient Connection
The PoE power budget is the total power available for distribution among connected devices. Each device has a specific power requirement, which should be within the switch’s power budget. A higher power budget allows for more device connections.
Power Per Port Considerations for High-Power Devices
Power per port refers to the maximum power distributed to a single port. A switch with a higher capacity per port accommodates devices with higher power requirements, like access points, IP cameras, and phones.
Key Features to Look for in Your PoE Switch
Consider these features for an efficient network setup:
Quality of Service (QoS): Prioritize critical traffic and improve network efficiency by ensuring the switch supports QoS features.
VLANs: Enhance security by segmenting your network and isolating traffic with VLANs.
Link Aggregation: Combine multiple ports into one logical connection for higher bandwidth and redundancy.
Management Interface: Ease configuration and management tasks with an intuitive and user-friendly interface.
Top PoE Switch Options for Your Business
Consider these reliable PoE switches: Cisco Catalyst 2960-L, Ubiquiti UniFi Switch 24, and NETGEAR ProSAFE Gigabit Smart Managed Switch. These switches balance cost-effectiveness, port density, and essential features.
Make an Informed Decision for Your Business with the Right PoE Switch
Choosing the right PoE switch is essential for network efficiency, security, and cost-effectiveness. Keep factors like PoE standards, port density, power budget, power per port, and key features in mind. With this knowledge, you can confidently select the perfect PoE switch for your business needs.
Recommended Reading: Passive WDM technology and its application in 4G/5G forward transmission
How to Set Up and Configure a Poe Switch
Enhance your network connectivity with a perfectly configured Poe switch. This comprehensive guide will walk you through the steps for setting up and optimizing your control and troubleshooting common issues.
PoE switch
Get Connected and Configured:
Connect the network cable from the switch’s Ethernet port to your router or modem.
Plug the PoE cable into the switch’s PoE port and connect it to your PoE device.
Please turn on the switch and wait for it to boot up.
Now, you can configure your Poe switch to meet your network requirements.
Power Your Devices with Injectors:
Connect the PoE injector by plugging the Ethernet cable into its input port.
Connect the other end of the cable to the switch’s PoE port.
Connect the PoE device to the injector’s output port.
Make sure the PoE device is receiving power.
Ethernet and PoE Cable Requirements:
Always use UTP Cat5e or higher-rated Ethernet cables for optimal performance.
Use PoE-compatible cables for your PoE devices.
Keep Ethernet cable length under 100 meters for stable network connectivity.
Troubleshooting Common Issues:
Avoid overloading your switch by not exceeding the maximum number of connected PoE devices.
Check the voltage capacity of your switch and ensure it is compatible with your PoE devices.
If experiencing unstable network connectivity, inspect Ethernet cables for any damage.
Manage VLANs and Network Segmentation:
Create VLANs to separate network segments and control traffic.
Improve network security with VLAN tagging for authorized device access.
Segment your network for better management and prevention of congestion.
Recommended Reading: Everything You Need to Know About Aggregation Switch
Frequently Asked Questions:
Embedded_World_2016,_korenix_PoE-Switche
Q: What is a PoE switch?
A: A PoE switch is a network switch that can provide electrical power over Ethernet cables. It allows devices like IP security cameras, wireless access points, and VoIP phones to receive power and data through a single Ethernet cable.
Q: How do I use a PoE switch?
A: To use a PoE switch, you connect your PoE-enabled devices to the control using Ethernet cables. The PoE switch will then provide power to these devices without needing separate power outlets.
Q: What are the benefits of PoE switches?
A: The benefits of PoE switches include simplified installation and maintenance, cost savings on electrical wiring and outlets, flexibility in device placement without the need for power outlets, and centralized power management through the switch.
Q: What are the applications of PoE switches?
A: PoE switches are commonly used in various applications such as IP surveillance, wireless networks, VoIP systems, access control systems, bright lighting, and IoT devices.
Q: What is the difference between a PoE switch and a regular switch?
A: The main difference between a PoE switch and a regular switch is that a PoE switch can provide power to PoE-enabled devices, while a normal switch does not. Standard switches only provide data connectivity.
Q: How does using PoE benefit me?
A: Using PoE means you can power your devices without needing power outlets. This allows for greater flexibility in device placement and eliminates the need for additional power cables and outlets.
Q: What are the main types of PoE?
A: The main types of PoE are original PoE (802.3af), PoE+ (802.3at), and high-power PoE (802.3bt). Each class provides different power levels and is compatible with other devices.
Q: What is a PoE injector?
A: A PoE injector is a device that adds PoE capability to a regular network switch. It injects power into the Ethernet cable, allowing PoE devices to receive power and data from the controller.
Q: What is a managed PoE switch?
A: A managed PoE switch is a PoE switch that provides advanced features and control over the network. It allows for better management of power allocation, prioritization of devices, and monitoring of network performance.
Q: How many ports do I need on a PoE switch?
A: The number of ports you need on a PoE switch depends on the number of PoE-powered devices you plan to connect. Choosing a switch with enough ports to accommodate all your devices is recommended, with room for future expansion.
|
{
"url": "https://ascentoptics.com/blog/what-is-poe-switch-everything-you-need-to-know/",
"source_domain": "ascentoptics.com",
"snapshot_id": "CC-MAIN-2024-30",
"warc_metadata": {
"Content-Length": "212474",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:VWET67HIYSXXTFLIGYPEMXV5ZKQ6F7HG",
"WARC-Concurrent-To": "<urn:uuid:cfa2a863-b595-4e8c-9eae-31ed9c462e2c>",
"WARC-Date": "2024-07-20T21:52:40Z",
"WARC-IP-Address": "104.21.80.183",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:MXHW2NGEWLAMDEWIE56LBMJ7CSHFPV4V",
"WARC-Record-ID": "<urn:uuid:7a40afa5-c209-4b6f-a11a-2283239928e3>",
"WARC-Target-URI": "https://ascentoptics.com/blog/what-is-poe-switch-everything-you-need-to-know/",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:a30385d0-3056-4000-94ab-20b50b0278ee>"
},
"warc_info": "isPartOf: CC-MAIN-2024-30\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for July 2024\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-168\r\nsoftware: Apache Nutch 1.20 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.5-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
25,
37,
38,
86,
87,
102,
116,
117,
160,
161,
404,
405,
450,
451,
794,
795,
1087,
1088,
1113,
1114,
1169,
1170,
1297,
1298,
1381,
1382,
1493,
1494,
1620,
1621,
1632,
1633,
1660,
1661,
1723,
1724,
1811,
1812,
1948,
1949,
2080,
2081,
2116,
2117,
2187,
2188,
2262,
2263,
2365,
2366,
2434,
2435,
2527,
2528,
2572,
2573,
2655,
2656,
2761,
2762,
2886,
2887,
3012,
3013,
3056,
3057,
3347,
3348,
3453,
3454,
3508,
3509,
3542,
3543,
3958,
3959,
3986,
3987,
4250,
4251,
4582,
4583,
4896,
4897,
4942,
4943,
5365,
5366,
5781,
5782,
5828,
5829,
6181,
6182,
6243,
6244,
6576,
6577,
6616,
6617,
6919,
6920,
6985,
6986,
7021,
7022,
7045,
7046,
7112,
7113,
7575,
7576,
7634,
7635,
8041,
8042,
8100,
8101,
8159,
8160,
8295,
8296,
8416,
8417,
8531,
8532,
8643,
8644,
8700,
8701,
8947,
8948,
9001,
9002,
9213,
9214,
9258,
9259,
9315,
9316,
9447,
9448,
9533,
9534,
9640,
9641,
9750,
9751,
9792,
9793,
10011,
10012,
10082,
10083,
10383,
10384,
10478,
10479,
10520,
10521,
10730,
10731,
10742,
10743,
10773,
10774,
10857,
10938,
10992,
11066,
11067,
11102,
11103,
11180,
11241,
11295,
11340,
11341,
11378,
11379,
11457,
11505,
11582,
11583,
11614,
11615,
11707,
11800,
11887,
11888,
11927,
11928,
11991,
12064,
12137,
12138,
12212,
12213,
12241,
12242,
12283,
12284,
12309,
12310,
12545,
12546,
12576,
12577,
12772,
12773,
12815,
12816,
13065,
13066,
13112,
13113,
13287,
13288,
13357,
13358,
13568,
13569,
13603,
13604,
13802,
13803,
13838,
13839,
14019,
14020,
14047,
14048,
14242,
14243,
14276,
14277,
14498,
14499,
14544,
14545
],
"line_end_idx": [
25,
37,
38,
86,
87,
102,
116,
117,
160,
161,
404,
405,
450,
451,
794,
795,
1087,
1088,
1113,
1114,
1169,
1170,
1297,
1298,
1381,
1382,
1493,
1494,
1620,
1621,
1632,
1633,
1660,
1661,
1723,
1724,
1811,
1812,
1948,
1949,
2080,
2081,
2116,
2117,
2187,
2188,
2262,
2263,
2365,
2366,
2434,
2435,
2527,
2528,
2572,
2573,
2655,
2656,
2761,
2762,
2886,
2887,
3012,
3013,
3056,
3057,
3347,
3348,
3453,
3454,
3508,
3509,
3542,
3543,
3958,
3959,
3986,
3987,
4250,
4251,
4582,
4583,
4896,
4897,
4942,
4943,
5365,
5366,
5781,
5782,
5828,
5829,
6181,
6182,
6243,
6244,
6576,
6577,
6616,
6617,
6919,
6920,
6985,
6986,
7021,
7022,
7045,
7046,
7112,
7113,
7575,
7576,
7634,
7635,
8041,
8042,
8100,
8101,
8159,
8160,
8295,
8296,
8416,
8417,
8531,
8532,
8643,
8644,
8700,
8701,
8947,
8948,
9001,
9002,
9213,
9214,
9258,
9259,
9315,
9316,
9447,
9448,
9533,
9534,
9640,
9641,
9750,
9751,
9792,
9793,
10011,
10012,
10082,
10083,
10383,
10384,
10478,
10479,
10520,
10521,
10730,
10731,
10742,
10743,
10773,
10774,
10857,
10938,
10992,
11066,
11067,
11102,
11103,
11180,
11241,
11295,
11340,
11341,
11378,
11379,
11457,
11505,
11582,
11583,
11614,
11615,
11707,
11800,
11887,
11888,
11927,
11928,
11991,
12064,
12137,
12138,
12212,
12213,
12241,
12242,
12283,
12284,
12309,
12310,
12545,
12546,
12576,
12577,
12772,
12773,
12815,
12816,
13065,
13066,
13112,
13113,
13287,
13288,
13357,
13358,
13568,
13569,
13603,
13604,
13802,
13803,
13838,
13839,
14019,
14020,
14047,
14048,
14242,
14243,
14276,
14277,
14498,
14499,
14544,
14545,
14774
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 14774,
"ccnet_original_nlines": 240,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.2851128876209259,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.019900500774383545,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.13738997280597687,
"rps_doc_frac_unique_words": 0.262967973947525,
"rps_doc_mean_word_length": 5.455119609832764,
"rps_doc_num_sentences": 134,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 5.316537380218506,
"rps_doc_word_count": 2217,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.141723170876503,
"rps_doc_frac_chars_dupe_6grams": 0.06160078942775726,
"rps_doc_frac_chars_dupe_7grams": 0.043492641299963,
"rps_doc_frac_chars_dupe_8grams": 0.026790140196681023,
"rps_doc_frac_chars_dupe_9grams": 0.012733589857816696,
"rps_doc_frac_chars_top_2gram": 0.031999338418245316,
"rps_doc_frac_chars_top_3gram": 0.014056559652090073,
"rps_doc_frac_chars_top_4gram": 0.008268560282886028,
"rps_doc_books_importance": -1319.627197265625,
"rps_doc_books_importance_length_correction": -1319.627197265625,
"rps_doc_openwebtext_importance": -607.5842895507812,
"rps_doc_openwebtext_importance_length_correction": -607.5842895507812,
"rps_doc_wikipedia_importance": -569.7117309570312,
"rps_doc_wikipedia_importance_length_correction": -569.7117309570312
},
"fasttext": {
"dclm": 0.5438977479934692,
"english": 0.8902292251586914,
"fineweb_edu_approx": 2.6138081550598145,
"eai_general_math": 0.13529843091964722,
"eai_open_web_math": 0.32302725315093994,
"eai_web_code": 0.19867318868637085
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.6",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "621.392",
"labels": {
"level_1": "Industrial arts, Technology, and Engineering",
"level_2": "Engineering",
"level_3": "Mechanical engineering and Machinery"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "4",
"label": "Missing Images or Figures"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "10",
"label": "Knowledge Article"
},
"secondary": {
"code": "23",
"label": "Tutorial"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "1",
"label": "General Audience"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
527,182,651,329,355,140
|
Logo
Search:
Sharepoint Forum
Ask Question UnAnswered
Home » Forum » Sharepoint RSS Feeds
Error while creating web site
Asked By: Jeramy Date: May 22 Category: Sharepoint Views: 919
I am here in some trouble.
I was in process of setting up my WSS test server for some development
work trials.
The installation process went smooth.
However when I try to migrate the site, it gives me the under given
error
Also if I create a new site and try to open the link, the moment it
should give the template pick screen it gives me the following error:-
Cannot connect to the configuration database. For tips on
troubleshooting this error, search for article 823287 in the Microsoft
Knowledge Base at http://support.microsoft.com
<http://support.microsoft.com/> .
I checked everything as per the article and it works fine.
It's a server farm installation and the SQL Server is on other machine.
Is there something I am missing?
Share:
3 Answers Found
Answer #1 Answered By: Bhumi Gokhale Answered On: May 22
How are you attempting to migrate the site?
Answer #2 Answered By: Vinay Thakur Answered On: May 22
Using smigrate......
The syntax is correct bkz it worked on my other WSS server ...
Answer #3 Answered By: Aakash Gavade Answered On: May 22
Could you clarify what you're attempting to migrate? Upon which SharePoint
services version? Additionally, if you could provide a text capture of the
error, that would help us as a group to help provide a course of action for
you.
Didn't find what you were looking for? Find more on Error while creating web site Or get search suggestion and latest updates.
Tagged:
|
{
"url": "http://www.go4sharepoint.com/Forum/error-while-creating-web-site-5380.aspx",
"source_domain": "www.go4sharepoint.com",
"snapshot_id": "crawl=CC-MAIN-2017-13",
"warc_metadata": {
"Content-Length": "28572",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:FCW6FLGVMU6ZKJNTAEVYOS3CPL3KY2VI",
"WARC-Concurrent-To": "<urn:uuid:346dad5e-986d-413e-9c5f-9a5b2ead6774>",
"WARC-Date": "2017-03-28T19:49:55Z",
"WARC-IP-Address": "198.252.71.136",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:TPZIR7MG5TSFKBKPQBXDINVESGRXXPRB",
"WARC-Record-ID": "<urn:uuid:3a959524-a6d3-4937-9e15-45520621ce2a>",
"WARC-Target-URI": "http://www.go4sharepoint.com/Forum/error-while-creating-web-site-5380.aspx",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:c57457ed-449e-4799-bd6a-cdbf6d5cc1ef>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-233-31-227.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2017-13\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web for March 2017\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
6,
14,
15,
32,
33,
59,
101,
102,
132,
133,
206,
207,
234,
305,
318,
356,
424,
430,
498,
569,
627,
698,
745,
779,
838,
910,
943,
944,
952,
953,
955,
956,
972,
973,
975,
1039,
1040,
1085,
1086,
1088,
1151,
1152,
1173,
1174,
1238,
1239,
1241,
1305,
1306,
1381,
1456,
1532,
1537,
1538,
1540,
1667,
1668,
1669,
1670,
1671,
1687,
1688,
1690
],
"line_end_idx": [
6,
14,
15,
32,
33,
59,
101,
102,
132,
133,
206,
207,
234,
305,
318,
356,
424,
430,
498,
569,
627,
698,
745,
779,
838,
910,
943,
944,
952,
953,
955,
956,
972,
973,
975,
1039,
1040,
1085,
1086,
1088,
1151,
1152,
1173,
1174,
1238,
1239,
1241,
1305,
1306,
1381,
1456,
1532,
1537,
1538,
1540,
1667,
1668,
1669,
1670,
1671,
1687,
1688,
1690,
1691
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 1691,
"ccnet_original_nlines": 63,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3333333432674408,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.030303029343485832,
"rps_doc_frac_lines_end_with_ellipsis": 0.03125,
"rps_doc_frac_no_alph_words": 0.18484848737716675,
"rps_doc_frac_unique_words": 0.5772058963775635,
"rps_doc_mean_word_length": 4.665441036224365,
"rps_doc_num_sentences": 21,
"rps_doc_symbol_to_word_ratio": 0.01818181946873665,
"rps_doc_unigram_entropy": 4.7863311767578125,
"rps_doc_word_count": 272,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.0394010990858078,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.01576044037938118,
"rps_doc_frac_chars_top_3gram": 0.030732860788702965,
"rps_doc_frac_chars_top_4gram": 0.03546098992228508,
"rps_doc_books_importance": -123.46817016601562,
"rps_doc_books_importance_length_correction": -111.02177429199219,
"rps_doc_openwebtext_importance": -83.98286437988281,
"rps_doc_openwebtext_importance_length_correction": -83.98286437988281,
"rps_doc_wikipedia_importance": -54.65492630004883,
"rps_doc_wikipedia_importance_length_correction": -44.789432525634766
},
"fasttext": {
"dclm": 0.0795903205871582,
"english": 0.8737144470214844,
"fineweb_edu_approx": 1.5195659399032593,
"eai_general_math": 0.00189024000428617,
"eai_open_web_math": 0.09362936019897461,
"eai_web_code": 0.000004410000201460207
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.445",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.776",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "2",
"label": "Click Here References"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "21",
"label": "Customer Support"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "2",
"label": "Partially Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-7,465,821,054,515,710,000
|
Intellipaat Back
Explore Courses Blog Tutorials Interview Questions
0 votes
3 views
in Python by (47.6k points)
I have a very long query. I would like to split it in several lines in Python. A way to do it in JavaScript would be using several sentences and joining them with a + operator (I know, maybe it's not the most efficient way to do it, but I'm not really concerned about performance in this stage, just code readability). Example:
var long_string = 'some text not important. just garbage to' + 'illustrate my example';
I tried doing something similar in Python, but it didn't work, so I used \ to split the long string. However, I'm not sure if this is the only/best/pythonicest way of doing it. It looks awkward. Actual code:
query = 'SELECT action.descr as "action", '\
'role.id as role_id,'\
'role.descr as role'\
'FROM '\
'Public.role_action_def,'\
'public.role,'\
'public.record_def, '\
'public.action'\
'WHERE role.id = role_action_def.role_id AND'\
'record_def.id = role_action_def.def_id AND'\
'action.id = role_action_def.action_id AND'\ 'role_action_def.account_id = ' + account_id + ' AND'\ 'record_def.account_id=' + account_id + ' AND'\
'def_id=' + def_id
1 Answer
0 votes
by (106k points)
edited by
Multi-line strings can be done easily, with the use of triple quotes to start and end them.
Following is the example that tells us how to use multi-line code:-
s = """ this is a very
long string if I had the
energy to type more and more ..."""
You can use single quotes too (3 of them of course at the start and end) and treat the resulting string just like any other string.
To know more about this you can have a look at the following video tutorial:-
Related questions
0 votes
1 answer
0 votes
1 answer
0 votes
1 answer
0 votes
2 answers
Browse Categories
...
|
{
"url": "https://intellipaat.com/community/2788/pythonic-way-to-create-a-long-multi-line-string",
"source_domain": "intellipaat.com",
"snapshot_id": "CC-MAIN-2024-33",
"warc_metadata": {
"Content-Length": "113165",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:BRB762VVUKOK2ME3YQTABF2AAQ7MPVUB",
"WARC-Concurrent-To": "<urn:uuid:01ff712c-de50-4597-bd39-730d428baaa3>",
"WARC-Date": "2024-08-03T16:57:04Z",
"WARC-IP-Address": "104.18.27.176",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:HQVQ3VIEKWPQXNXH7J3CTOHAEWBMI3GK",
"WARC-Record-ID": "<urn:uuid:67ee402a-15c2-483c-9bf4-035ad5fd576c>",
"WARC-Target-URI": "https://intellipaat.com/community/2788/pythonic-way-to-create-a-long-multi-line-string",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:923e17be-4a66-428a-9af5-60bf3e9e922f>"
},
"warc_info": "isPartOf: CC-MAIN-2024-33\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for August 2024\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-211\r\nsoftware: Apache Nutch 1.20 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.5-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
17,
18,
69,
77,
85,
113,
114,
442,
443,
531,
532,
740,
741,
786,
787,
811,
812,
835,
836,
846,
847,
874,
875,
892,
893,
917,
918,
936,
937,
985,
986,
1032,
1033,
1182,
1183,
1202,
1203,
1212,
1213,
1221,
1238,
1248,
1249,
1341,
1342,
1410,
1411,
1435,
1436,
1469,
1470,
1513,
1514,
1646,
1647,
1725,
1726,
1744,
1745,
1753,
1762,
1770,
1779,
1787,
1796,
1804,
1814,
1815,
1833,
1834
],
"line_end_idx": [
17,
18,
69,
77,
85,
113,
114,
442,
443,
531,
532,
740,
741,
786,
787,
811,
812,
835,
836,
846,
847,
874,
875,
892,
893,
917,
918,
936,
937,
985,
986,
1032,
1033,
1182,
1183,
1202,
1203,
1212,
1213,
1221,
1238,
1248,
1249,
1341,
1342,
1410,
1411,
1435,
1436,
1469,
1470,
1513,
1514,
1646,
1647,
1725,
1726,
1744,
1745,
1753,
1762,
1770,
1779,
1787,
1796,
1804,
1814,
1815,
1833,
1834,
1837
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 1837,
"ccnet_original_nlines": 70,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.33740830421447754,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.04156478866934776,
"rps_doc_frac_lines_end_with_ellipsis": 0.014084509573876858,
"rps_doc_frac_no_alph_words": 0.2982885241508484,
"rps_doc_frac_unique_words": 0.5379061102867126,
"rps_doc_mean_word_length": 4.765343189239502,
"rps_doc_num_sentences": 27,
"rps_doc_symbol_to_word_ratio": 0.004889979958534241,
"rps_doc_unigram_entropy": 4.74818754196167,
"rps_doc_word_count": 277,
"rps_doc_frac_chars_dupe_10grams": 0.034090910106897354,
"rps_doc_frac_chars_dupe_5grams": 0.034090910106897354,
"rps_doc_frac_chars_dupe_6grams": 0.034090910106897354,
"rps_doc_frac_chars_dupe_7grams": 0.034090910106897354,
"rps_doc_frac_chars_dupe_8grams": 0.034090910106897354,
"rps_doc_frac_chars_dupe_9grams": 0.034090910106897354,
"rps_doc_frac_chars_top_2gram": 0.027272729203104973,
"rps_doc_frac_chars_top_3gram": 0.024242419749498367,
"rps_doc_frac_chars_top_4gram": 0.039393939077854156,
"rps_doc_books_importance": -172.93490600585938,
"rps_doc_books_importance_length_correction": -172.0052032470703,
"rps_doc_openwebtext_importance": -91.0098876953125,
"rps_doc_openwebtext_importance_length_correction": -91.0098876953125,
"rps_doc_wikipedia_importance": -75.48814392089844,
"rps_doc_wikipedia_importance_length_correction": -75.48641967773438
},
"fasttext": {
"dclm": 0.30193525552749634,
"english": 0.9042200446128845,
"fineweb_edu_approx": 2.217602491378784,
"eai_general_math": 0.7154757380485535,
"eai_open_web_math": 0.44796520471572876,
"eai_web_code": 0.21768832206726074
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1332",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.133",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "2",
"label": "Click Here References"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "23",
"label": "Tutorial"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
8,418,576,977,170,111,000
|
5
I have a Blockchain wallet but am unable to decrypt my wallet and login. I created the wallet on OSX and am trying to login on a PC but it's not working.
• What are my options to brute force this account, when I know most of the characters involved?
I'm a programmer, and can write the code, so knowing what URLs and data files I need to work with would be a help.
3
You can wrap a brute-force wrapper around any of the answers here. Just write some loops that iterate on all possible passwords, and call one of the functions in the linked question to try and decrypt you wallet.
This is what I used in a similar scenario (Javascript/node.js).
• 1
This was perfect... I was able to install Node.JS on OSX and cracked it... execution time was 5 seconds. – goodguys_activate Sep 1 '13 at 13:06
• @makerofthings7 terrific! – ripper234 Sep 1 '13 at 15:51
• So does this mean someone internal at blockchain.info who has access to encrypted wallets could decrypt them by brute force in a small amount of time with limited computing power? – Fraggle Jun 15 '14 at 12:19
• @Fraggle only if the password was weak to begin with. In my case, my friend who lost his wallet pass had some ideas on the password, but at the end the brute-forcing effort we did didn't work out :( – ripper234 Jun 22 '14 at 10:21
protected by Community Dec 9 '17 at 0:55
Thank you for your interest in this question. Because it has attracted low-quality or spam answers that had to be removed, posting an answer now requires 10 reputation on this site (the association bonus does not count).
Would you like to answer one of these unanswered questions instead?
Not the answer you're looking for? Browse other questions tagged or ask your own question.
|
{
"url": "https://bitcoin.stackexchange.com/questions/12762/how-can-i-brute-force-decrypt-my-blockchain-wallet/12792",
"source_domain": "bitcoin.stackexchange.com",
"snapshot_id": "crawl=CC-MAIN-2019-43",
"warc_metadata": {
"Content-Length": "131009",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:B6HV6FEJNEFQWW5DWEXU2YIDC7IYSV3K",
"WARC-Concurrent-To": "<urn:uuid:a52db9b3-13ef-499c-b60d-fee6e38cfcc3>",
"WARC-Date": "2019-10-14T04:25:54Z",
"WARC-IP-Address": "151.101.193.69",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:2KQDTTQCZ2JYP4XM2V7EO2YIFB5IUIEZ",
"WARC-Record-ID": "<urn:uuid:281e6029-1648-4e38-b513-ba45fe57b2fe>",
"WARC-Target-URI": "https://bitcoin.stackexchange.com/questions/12762/how-can-i-brute-force-decrypt-my-blockchain-wallet/12792",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:d4fc03d2-3e90-4dea-a53c-97b5dc0b9138>"
},
"warc_info": "isPartOf: CC-MAIN-2019-43\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for October 2019\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-52.ec2.internal\r\nsoftware: Apache Nutch 1.16 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.1-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
2,
3,
157,
158,
256,
257,
372,
373,
375,
376,
589,
590,
654,
655,
661,
809,
870,
1084,
1319,
1320,
1361,
1362,
1583,
1584,
1652,
1653
],
"line_end_idx": [
2,
3,
157,
158,
256,
257,
372,
373,
375,
376,
589,
590,
654,
655,
661,
809,
870,
1084,
1319,
1320,
1361,
1362,
1583,
1584,
1652,
1653,
1743
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 1743,
"ccnet_original_nlines": 26,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.4088541567325592,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.02864583022892475,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.2213541716337204,
"rps_doc_frac_unique_words": 0.5867508053779602,
"rps_doc_mean_word_length": 4.233438491821289,
"rps_doc_num_sentences": 21,
"rps_doc_symbol_to_word_ratio": 0.005208330228924751,
"rps_doc_unigram_entropy": 4.958174228668213,
"rps_doc_word_count": 317,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.011177349835634232,
"rps_doc_frac_chars_top_3gram": 0.011922500096261501,
"rps_doc_frac_chars_top_4gram": 0.011922500096261501,
"rps_doc_books_importance": -176.75970458984375,
"rps_doc_books_importance_length_correction": -167.2028350830078,
"rps_doc_openwebtext_importance": -102.58424377441406,
"rps_doc_openwebtext_importance_length_correction": -102.58424377441406,
"rps_doc_wikipedia_importance": -89.2197265625,
"rps_doc_wikipedia_importance_length_correction": -83.73792266845703
},
"fasttext": {
"dclm": 0.10938048362731934,
"english": 0.9559754133224487,
"fineweb_edu_approx": 1.2297135591506958,
"eai_general_math": 0.3974616527557373,
"eai_open_web_math": 0.23515993356704712,
"eai_web_code": 0.0037931199185550213
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.82",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.678",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "4",
"label": "Missing Images or Figures"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "4",
"label": "Graduate/Expert Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-103,805,676,583,239,310
|
6.0.0-git
2019-12-15
Last Modified 2010-01-09 by Jan Schneider
Turba, the Horde Address Book
Turba can be configured to provide multiple address books from multiple backends. This is done in turba/config/sources.php.
Supported backends are:
Nomenclature and architecture
• Turba can manage any number of different sources, each source can use a different backend driver like LDAP or SQL and utilize a different address book scheme. Administrators can set permissions for each source.
• SQL sources can be used as a backend for shares. These are address books that each users can create and share with other users and groups.
• The user can also create (shareable) virtual address books, which are basically saved searches.
• All those, i.e. non-shared sources, the shares that the user has permissions for, and the user's virtual address books appear as address books in the user's interface.
• The user can further create distribution list next to regular contacts in any address book that he has write access to. Distribution lists can contain contacts from any available address book, but other users can of course only see those contacts in the list that they also have permissions for.
Arbitrary information
[Turba 2.1 and later]: For shared address books add the following to the bottom stanza of the source declaration:
'use_shares' => true,
When using the shared address book functionality, user and group permissions are managed directly by the user who owns the address book using the My Address Books interface in Turba, not by an administrator using the Administration/Permissions panel. Extended permissions (such as Maximum Number of Contacts) may still be set via the Administration/Permissions panel.
For sources not using the shared address book functionality, all permissions can be structured through the Administration/Permissions panel.
Hit the icon next to All Permissions to add the new top level permissions for Address Book (turba).
Select the key icon next to Address Book (turba) and add permissions for the Sources.
Select the key icon next to Sources and add the address book you want to establish permissions for.
Select the notepad icon to modify the permissions on the address book. In order for the groups to work you must have the DataTree tied to a valid source (SQL or hooks) or LDAP.
External Links
Syncing the iPhone addressbook with Horde: http://edeca.net/wp/2010/01/syncing-the-iphone-addressbook-with-horde/
Modifying fields in the Turba addressbook: http://edeca.net/wp/2010/01/modifying-fields-in-the-turba-addressbook/
Someone's OpenLDAP/Turba howto: http://web.archive.org/web/20060708192705/http://ww2.redant.ca/consulting/ldap/turba.php
|
{
"url": "https://wiki.horde.org/TurbaModule",
"source_domain": "wiki.horde.org",
"snapshot_id": "crawl=CC-MAIN-2019-51",
"warc_metadata": {
"Content-Length": "13253",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:IUCOIEHPJF7RMJSFD7URKCRCJYQMSYUJ",
"WARC-Concurrent-To": "<urn:uuid:b1e1b227-0888-4b9c-a5f7-b2602f04e16b>",
"WARC-Date": "2019-12-15T16:33:45Z",
"WARC-IP-Address": "78.47.133.137",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:JM4E22GOXP544S2DDAGBW4QACMH5J55L",
"WARC-Record-ID": "<urn:uuid:0dbf7d2f-6f02-4b5c-a90e-16349fb0d227>",
"WARC-Target-URI": "https://wiki.horde.org/TurbaModule",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:9be9b835-7cdb-488c-9cb7-e764f3c20ce2>"
},
"warc_info": "isPartOf: CC-MAIN-2019-51\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for December 2019\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-48.ec2.internal\r\nsoftware: Apache Nutch 1.16 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.1-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
10,
21,
63,
64,
94,
95,
219,
220,
244,
245,
275,
276,
491,
634,
734,
906,
1206,
1207,
1229,
1230,
1344,
1345,
1371,
1372,
1740,
1741,
1882,
1883,
1983,
1984,
2070,
2071,
2171,
2172,
2349,
2350,
2365,
2366,
2480,
2594
],
"line_end_idx": [
10,
21,
63,
64,
94,
95,
219,
220,
244,
245,
275,
276,
491,
634,
734,
906,
1206,
1207,
1229,
1230,
1344,
1345,
1371,
1372,
1740,
1741,
1882,
1883,
1983,
1984,
2070,
2071,
2171,
2172,
2349,
2350,
2365,
2366,
2480,
2594,
2714
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 2714,
"ccnet_original_nlines": 40,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3254972994327545,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.009041589684784412,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.2296564131975174,
"rps_doc_frac_unique_words": 0.4234693944454193,
"rps_doc_mean_word_length": 5.5459184646606445,
"rps_doc_num_sentences": 32,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.614243507385254,
"rps_doc_word_count": 392,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.05519779026508331,
"rps_doc_frac_chars_dupe_6grams": 0.05519779026508331,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.0556577704846859,
"rps_doc_frac_chars_top_3gram": 0.022079119458794594,
"rps_doc_frac_chars_top_4gram": 0.010119600221514702,
"rps_doc_books_importance": -274.7345275878906,
"rps_doc_books_importance_length_correction": -274.7345275878906,
"rps_doc_openwebtext_importance": -140.20892333984375,
"rps_doc_openwebtext_importance_length_correction": -140.20892333984375,
"rps_doc_wikipedia_importance": -86.73623657226562,
"rps_doc_wikipedia_importance_length_correction": -86.73623657226562
},
"fasttext": {
"dclm": 0.09353358298540115,
"english": 0.8731749653816223,
"fineweb_edu_approx": 2.2529959678649902,
"eai_general_math": 0.2219768762588501,
"eai_open_web_math": 0.04178011044859886,
"eai_web_code": 0.675572395324707
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.467",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.74",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "2",
"label": "Click Here References"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "23",
"label": "Tutorial"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "4",
"label": "Graduate/Expert Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
3,252,803,760,689,019,000
|
Difference Between NVIDIA GTX and RTX
Difference Between NVIDIA GTX And RTX
Share on facebook
Share on twitter
Share on linkedin
Share on pinterest
Share on telegram
Share on whatsapp
Share on email
Are you a gaming lover and want to build a gaming computer or do you want to replace the graphics processing unit (GPU) in your current computer? So obviously, you will be looking for a better, faster, and more efficient computer. There are two popular types in front of you: GTX and RTX.
NVIDIA is a tech giant, especially in graphics cards/computer processors and many other areas. Turing’s GPU architecture powers the GeForce RTX 20-Series and GTX 16-Series cards. As the world’s most advanced architecture, Turing brings next-generation cinema technology to the latest games with exceptional performance and efficiency.
I will take a look at the new features provided by Turing Architecture to see if any of them could be a game-changer. For example, DLSS (Deep Learning Super-Sampling) can provide a significant performance boost on supported headers.
After this short discussion of features, I will walk you through the performance comparison between RTX and GTX, so you can see how these two cards compare between games.
I will end with a few comments on pricing and availability, which will obviously also have a significant impact on your purchase decision. Without further ado, let’s compare the Difference Between GTX And RTX!
Is The RTX Same As The GTX?
Nvidia’s new 20 series cards are called RTX cards rather than GTX, which refers to the card’s real-time ray tracing capabilities. Ray tracing refers to a process of simulating light as it realistically bounces off a scene, allowing for more realistic-looking light and greater graphic fidelity through shadows.
Read Also How to Connect to 5 GHz wifi Windows 10
GTX (Giga Texel Shader eXtreme)
GTX stands for Giga Texel Shader eXtreme and is a variant of the GeForce brand owned by Nvidia. Nvidia uses the GTX suffix to mark its best cards.
It wouldn’t be fair to say that this trend continued until the RTX cards were released, as Nvidia gradually began to increase the number of GTX-branded cards. They were first introduced in 2008 with the 200 Series, codenamed Tesla. The first product in this series was the GTX 260 and the more expensive GTX 280.
Although the 200 series cards are technically related to GTX cards, the latest GTX 16 series include the GTX 1650, GTX 1660, GTX 1660Ti, and their Super counterparts. These are based on Turing architecture and were introduced in 2019.
Although the performance margin is not much different, the price difference is so high that it cannot be ignored. So if you’re looking to get a GTX card, the GTX 1600 series should be a no-brainer. However, it has some major drawbacks compared to RTX cards.
Read Also 10 Best 120 Inch Motorized Projector Screen
RTX (Ray Tracing Texel eXtreme)
RTX stands for Ray Tracing Texel Extreme and is also a variant of GeForce. NVIDIA RTX graphics cards are the first to include RT cores. This dedicated ray-tracing hardware can produce 10 gigabytes of rays per second, enabling real-time movie-like lighting in games. Real-time ray tracing is only possible because RTX graphics cards provide 6x faster ray tracing performance.
Above is a view of Metro Exodus showing the immersive details obtained from ray tracing in real-time. Click on the image and then move the slider between “RTX On” and “RTX Off” to see the difference in lighting.
RTX graphics cards are the first to feature tensioner cores capable of delivering over 100 teraflops of AI processing to accelerate gaming performance with NVIDIA DLSS. These RTX cards include the RTX 2060, RTX 2070, RTX 2080, RTX 2080Ti, and the Super 2060 and 2070 equivalents.
For those looking for a gaming GPU that handles the next generation of immersive gaming titles, the RTX is a great way to go.
Read Also 15 Best Wireless HDMI Transmitter
Architecture Of GTX And RTX
GPU architecture is important and includes how well the GPU will perform in the game. This includes things like clock speed, performance, and how the graphics look in general.
When it comes to the architecture of the RTX and GTX series, there is surprisingly little difference between the two. When looking at the new models, they both use the Nvidia Turing architecture. It is built specifically for the new Nvidia series and has the best architecture available today.
Nvidia Turing offers much better performance than older Nvidia GPUs. Overall it runs quiet and quiet. It is 1.4 times more energy efficient than the previous models and the graphics rendered are particularly spectacular.
While most GTX cards use the Nvidia Turing architecture, older series, such as 1060, for example, use Nvidia Pascal. Although this architecture is good, it does not give such good performance as compared to the RTX series.
Overall, the RTX model has better core and clock performance, allowing for better gaming performance than the GTX series. They also have Nvidia DLSS and ray tracing cores, which the GTX doesn’t have.
Read Also 10 Best Ultra Widescreen Monitors For Gaming
The difference in the performance of GTX and RTX
The RTX (20 series) cards and 16 series GTX cards are based on the Turing architecture. GTX 10 series cards are based on Pascal architecture.
Pascal architecture uses 16nm transistors and Turing architecture uses 12nm transistors. Smaller transistors allow you to fit more of them on the processor, and this is directly related to better performance. Turing cards are 6 times faster than Pascal cards in ray tracing. They provide 30 percent better performance than Pascal cards in general.
Turing cards support GDDR6 memory types, while Pascal cards support GDDR5, GDDR5X, GDDR4 memory types. This makes RTX cards superior in memory-related applications, including high memory bandwidth, most games, and some deep learning and video processing applications. The TDP rating of RTX cards is lower than that of GTX cards, thanks to the tuning architecture, this makes them more efficient and helps you save some energy costs.
Here is a little information. Although the 16 Series cards are also based on the Turing architecture, they do not have RT cores or tensioner cores to help with real-time ray tracing, although Nvidia released a driver update to support ray tracing on them. It has adequate hardware and therefore performs poorly in ray tracing applications compared to RTX cards.
Cost
The cost of each card depends on the version you want to use, as different manufacturers offer different versions of the GPU. The short answer is that the RTX 2080 is currently cheaper than the GTX 1080 Ti.
Amazon has something in the ballpark for $ 900, like this EVGA GTX 1080 Ti for $ 980. Again, this is a great card with great cooling technology and fancy RGB lighting, but it costs $ 300 more than many GPUs. RTX 2080 and does not have ray tracing or DLSS support. It’s slightly less expensive than the M 1080 Ti at $ 930, but it’s still a bit more expensive than the RTX 2080.
Read Also 6 Best Wireless Headphones for TV
Which is better RTX 2060 or GTX 1660?
The RTX 2060 stands out as the fastest card, with additional CUDA cores and faster memory. Both cards easily recorded 60 frames per second, which equates to Ultra quality settings with most mainstream games. This is impressive for the GTX 1660 Ti, as it rises above the previous GTX 1070 in this regard.
Why are GPUs so expensive now in 2021?
The latest GPUs from Nvidia and AMD were nearly impossible to buy in 2021 when COVID-19 hit manufacturing and supply chains. Retailers typically sell out in seconds every time they restock, thanks to resellers and cryptocurrency miners who have bought more and more graphics cards using bots.
Conclusion
In short, Nvidia introduced the RTX designation primarily for marketing, making its 20-series Turing GPUs look like a much bigger upgrade than they actually are.
Considering all of the above, we wouldn’t say that RTX GPUs can only be achieved for ray tracing and DLSS, and performance per dollar should always come first, especially if you want to get the best value for your money.
Amazon Site is a participant of the Amazon Services LLC Associates Program, an affiliate advertising program that is designed to provide aid for the websites in earning an advertisement fee by means of advertising and linking to Amazon products.
BEST WIRELESS DEVICES
Best Wireless Devices
CATEGORIES
RECENT ARTICLES
Ⓒ COPYRIGHT 2021| BEST WIRELESS DEVICES
Avatar of Akbar Sheikh
About Author
An engineer and MBA, who is a technology and a gadget freak. I write about smart home solutions and gadgets like all wireless devices, technology brands like Apple. Love to follow the latest trends in the technology space and write about latest developments.
Latest
0 Shares
|
{
"url": "https://bestwirelessdevices.com/difference-between-nvidia-gtx-and-rtx/",
"source_domain": "bestwirelessdevices.com",
"snapshot_id": "CC-MAIN-2023-06",
"warc_metadata": {
"Content-Length": "202712",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:CN4S7QZSYPGTSMJ5HMBVM5D7R7YKIIZI",
"WARC-Concurrent-To": "<urn:uuid:55abe2cd-b794-4dc6-848c-268df2448d38>",
"WARC-Date": "2023-02-01T19:46:12Z",
"WARC-IP-Address": "35.208.138.97",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:WMWHHL7XONGZQ537I4TP4KJ5ZKBPI5EU",
"WARC-Record-ID": "<urn:uuid:68ded5ea-4403-4e8a-a9c5-b58a34e6146f>",
"WARC-Target-URI": "https://bestwirelessdevices.com/difference-between-nvidia-gtx-and-rtx/",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:226532e3-ba41-4d5c-a8ed-938cc9025e5d>"
},
"warc_info": "isPartOf: CC-MAIN-2023-06\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for January/February 2023\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-225\r\nsoftware: Apache Nutch 1.19 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.4-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
38,
39,
77,
78,
96,
113,
131,
150,
168,
186,
201,
202,
491,
492,
827,
828,
1061,
1062,
1233,
1234,
1444,
1445,
1473,
1474,
1785,
1786,
1836,
1837,
1869,
1870,
2017,
2018,
2331,
2332,
2567,
2568,
2826,
2827,
2882,
2883,
2915,
2916,
3291,
3292,
3504,
3505,
3785,
3786,
3912,
3913,
3957,
3958,
3986,
3987,
4163,
4164,
4458,
4459,
4680,
4681,
4904,
4905,
5105,
5106,
5161,
5162,
5211,
5212,
5354,
5355,
5703,
5704,
6137,
6138,
6500,
6501,
6506,
6507,
6714,
6715,
7092,
7093,
7137,
7138,
7176,
7177,
7481,
7482,
7521,
7522,
7815,
7816,
7827,
7828,
7990,
7991,
8212,
8213,
8459,
8460,
8482,
8483,
8505,
8506,
8517,
8518,
8534,
8535,
8575,
8598,
8611,
8870,
8871,
8878,
8879
],
"line_end_idx": [
38,
39,
77,
78,
96,
113,
131,
150,
168,
186,
201,
202,
491,
492,
827,
828,
1061,
1062,
1233,
1234,
1444,
1445,
1473,
1474,
1785,
1786,
1836,
1837,
1869,
1870,
2017,
2018,
2331,
2332,
2567,
2568,
2826,
2827,
2882,
2883,
2915,
2916,
3291,
3292,
3504,
3505,
3785,
3786,
3912,
3913,
3957,
3958,
3986,
3987,
4163,
4164,
4458,
4459,
4680,
4681,
4904,
4905,
5105,
5106,
5161,
5162,
5211,
5212,
5354,
5355,
5703,
5704,
6137,
6138,
6500,
6501,
6506,
6507,
6714,
6715,
7092,
7093,
7137,
7138,
7176,
7177,
7481,
7482,
7521,
7522,
7815,
7816,
7827,
7828,
7990,
7991,
8212,
8213,
8459,
8460,
8482,
8483,
8505,
8506,
8517,
8518,
8534,
8535,
8575,
8598,
8611,
8870,
8871,
8878,
8879,
8887
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 8887,
"ccnet_original_nlines": 115,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3666275143623352,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.07226791977882385,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.14864864945411682,
"rps_doc_frac_unique_words": 0.35883548855781555,
"rps_doc_mean_word_length": 4.857142925262451,
"rps_doc_num_sentences": 78,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 5.491461277008057,
"rps_doc_word_count": 1477,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.03317536041140556,
"rps_doc_frac_chars_dupe_6grams": 0.01700584962964058,
"rps_doc_frac_chars_dupe_7grams": 0.008084749802947044,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.019514910876750946,
"rps_doc_frac_chars_top_3gram": 0.007527180016040802,
"rps_doc_frac_chars_top_4gram": 0.007248399779200554,
"rps_doc_books_importance": -816.88916015625,
"rps_doc_books_importance_length_correction": -816.88916015625,
"rps_doc_openwebtext_importance": -439.332763671875,
"rps_doc_openwebtext_importance_length_correction": -439.332763671875,
"rps_doc_wikipedia_importance": -320.3525390625,
"rps_doc_wikipedia_importance_length_correction": -320.3525390625
},
"fasttext": {
"dclm": 0.10249984264373779,
"english": 0.9401657581329346,
"fineweb_edu_approx": 1.8221532106399536,
"eai_general_math": 0.10884398221969604,
"eai_open_web_math": 0.14993876218795776,
"eai_web_code": 0.027122439816594124
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.16",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "-1",
"labels": {
"level_1": "",
"level_2": "",
"level_3": ""
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "4",
"label": "Analyze"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "14",
"label": "Reviews/Critiques"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "4",
"label": "Missing Images or Figures"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "10",
"label": "Knowledge Article"
},
"secondary": {
"code": "17",
"label": "Product Page"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "1",
"label": "General Audience"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
929,365,687,428,938,400
|
2003-08-22 – The ultimate flaw in biometric security – you!
\”That realization dawned on [Berry] when he called Det. Dave Harned, a veteran in the Commercial Crimes Division of the Los Angeles Police Department.
Harned takes all the calls about identity theft and directs them to the right place.
His department has resources to investigate only a tiny fraction of the 100-plus identity theft complaints it receives every day.\”
The quote above is taken from a very long article available here about a man in the United States who had his identity stolen by a murderer. Perhaps needless to say, it has wrecked his credit, upset him, and it is still a full-time job sorting it out a year later.
Now imagine if it was a hundred times worse… Mr. Berry could prove he wasn’t the same guy quite easily, as he was a big white man, and Hunter, the con-man, was afro-carribean. Besides which, the conman had access to very little of Berry’s information, and the nature of the dozens of places that were tricked is such that there was, thankfully, no definitive ID question and answer. This alone meant that Berry could prove that he wasn’t the con-man, as the address was wrong, etc. However, he says it is still a full time job trying to correct everything.
With the new panic about terrorism, however, all that is likely to change. Modern PC fingerprint scanners are easily available for less than $100/£50 and they plug right into the nearest USB port. Iris scanning webcams are also less than £25, including the software. This has inspired the politicians to try to get everyone to have a unique ID card, some ultimate form of ID that is \”perfect\”. What could be better than a thumbprint?
As it turns out, almost anything…
Imagine if you mugged me, or pickpocketed me, and got a hold of my keys. I carry a lot of keys, and they have no link to me, except through a blind-drop 3rd party, who hold my name and address and promise to send them back to me should they wind up in a postbox. No-one can get my address from them, without knowing who I am, and even then, they will be of little use, since I would know that the physical keys had been compromised. After all, it would take at least half an hour to copy them, and I always know where, exactly, my keys are. So, if you turned up at my house, I would catch you, and beat you within an inch of your life, if you were lucky. If you were smart, and waited till I was out, surprise! I changed the locks! The many layers of physical security were not breached at any time, but I had to spend a fortune changing my locks (but the house insurance has locks cover)
Now, imagine if the key was totally unique, and everyone knew it was unique, and therefore it was a \”perfect\” security device. These are how the biometric security crowd hope to convince us that we should all form an orderly queue in front of the machine and have a barcode burned into our skin. Sorry, have our retinas scanned and our fingerprints taken, then locked into a card with a sample of DNA to confirm who we are, all of which goes into a big government database. A government that can’t even set up a system so doctors can email each other for £5 million pounds, but that wants us all to be happy to pay £36 for this mandatory card.
So let us assume that we are good sheep, and that we do this. For the next few years, everything is hunky-dory, and all the bad people get caught just before chopping of a person’s finger or gougeing an eye, or as is more likely, that the shop assistant spots it at point of sale, except that many will be ATMs or other automatic systems. But let us assume this is true.
Now, you go to the machine one day, and it says that you have no money left in your bank accont, nor your credit card. This is bad, since you got paid three days ago. So you contact the bank, and they tell you that you got your money out from an ATM 300 miles away from where you normally hang out. They tell you the exact time, the amount, and that you verified it with a fingerprint. You complain, so they involve the police, and you go in to the bank for an interview, Mr. Plod coming along too.
At the branch, you go up to a room, and you see a video of yourself, apparently, in grainy CCTV, walk up to a place you have never been, press your finger to the ATM to confirm you are who you say you are, withdraw all your money, then leave. You protest, saying you can prove that you weren’t ever there, so the bank has you arrested for attempted fraud.
Now, dear reader, how could such a thing happen?
Imagine if you had an infinite number of copies of your front door key, each with your address tagged nicely to it. You would probably lose a few, and after a while you would get careless, and, since they are infinite, how could you tell if you dropped one somewhere? Especially if the keys were really small, or almost invisible?
Not to push the analogy too far, but that is exactly what you do every single time you touch anything. Your DNA slews off from your body everywhere you go, and everything you touch that is even remotely smooth leaves behind a set of prints for the enterprising identity theif to walk away with. He doesn’t even need to know who the print belongs to at the time, since he could easily take your photo with his phone, then run another idenity matching system to ID you from your face. He takes your glass, or even a photo of your hand holding the glass, and bingo! One iron clad fake ID!
What next? Well, once a fake slip-on latex mould of your print was ready, your identity is ready to sell to the highest bidder. Put simply, anyone who was nearly your physical description, or looked a bit like you, would bid highly for your prints and a mugshot, plus all the usual info that scammers like to get.
The next step is almost too easy. Wait till dark, then go to the shops. Grow a bit of stubble, change your hair to match, whatever… A wig could be your first big purchase! Or even some customised contacts that just *happen* to match the iris scan of your victim… All verified by the fake fingerprint and general matching of appearance. Needless to say, generally you wouldn’t need to match the photo, unless it was a higher level of security.
So, as the victim here, how do you:
1. know your identity has been stolen? (the keys are invisible, yet public)
2. prove you didn’t have anything to do with it? (that it isn’t you trying a fraud)
3. change your keys? (My fingers are quite firmly attached, thank you!)
These are the most obvious issues. Good personal security of your biometrics might be a help, but you are still going to have to give that data away a hundred times a week, and remember, it is generally the shop staff on minimum wage that steal credit card numbers, so who will be surprized when they start selling iris scans?
As far as I can see, this is a fatal flaw with 90%+ of biometric systems. Don’t even get me started on computer log-ons that try to follow you around the room by your laugh… The only funny thing about that is that someone funded the study!
In summary, the ultimate flaw in biosecurity is the lack of key revocation. Until someone fixes this problem, biometrics will be open to abuse. This is likely to be unsolvable.
Leave a Comment
|
{
"url": "https://rubbertreeplant.co.uk/archives/327",
"source_domain": "rubbertreeplant.co.uk",
"snapshot_id": "crawl=CC-MAIN-2019-04",
"warc_metadata": {
"Content-Length": "34665",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:GVQ5QXSDCVUVDXZA7H4X4D44Y7ZBXAGP",
"WARC-Concurrent-To": "<urn:uuid:2d87802e-1327-4ede-934d-060b5101f59a>",
"WARC-Date": "2019-01-20T17:57:32Z",
"WARC-IP-Address": "185.119.173.158",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:SJKKTQH4WS42HDKSRESXU4RYK3CGWGPG",
"WARC-Record-ID": "<urn:uuid:882cc700-1c2c-4362-800a-c8a63333affb>",
"WARC-Target-URI": "https://rubbertreeplant.co.uk/archives/327",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:135316a1-f1ce-4b6a-86d7-93f1d37b3665>"
},
"warc_info": "isPartOf: CC-MAIN-2019-04\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for January 2019\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-146-180-207.ec2.internal\r\nsoftware: Apache Nutch 1.15 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 0.11-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
60,
61,
213,
214,
299,
300,
432,
433,
698,
699,
1256,
1257,
1693,
1694,
1728,
1729,
2618,
2619,
3265,
3266,
3637,
3638,
4137,
4138,
4494,
4495,
4544,
4545,
4876,
4877,
5463,
5464,
5778,
5779,
6222,
6223,
6259,
6260,
6338,
6424,
6498,
6499,
6826,
6827,
7067,
7068,
7245,
7246,
7247
],
"line_end_idx": [
60,
61,
213,
214,
299,
300,
432,
433,
698,
699,
1256,
1257,
1693,
1694,
1728,
1729,
2618,
2619,
3265,
3266,
3637,
3638,
4137,
4138,
4494,
4495,
4544,
4545,
4876,
4877,
5463,
5464,
5778,
5779,
6222,
6223,
6259,
6260,
6338,
6424,
6498,
6499,
6826,
6827,
7067,
7068,
7245,
7246,
7247,
7262
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 7262,
"ccnet_original_nlines": 49,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.4984404146671295,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.014348099939525127,
"rps_doc_frac_lines_end_with_ellipsis": 0.019999999552965164,
"rps_doc_frac_no_alph_words": 0.15283842384815216,
"rps_doc_frac_unique_words": 0.40740740299224854,
"rps_doc_mean_word_length": 4.199259281158447,
"rps_doc_num_sentences": 71,
"rps_doc_symbol_to_word_ratio": 0.0031191499438136816,
"rps_doc_unigram_entropy": 5.599566459655762,
"rps_doc_word_count": 1350,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.005291940178722143,
"rps_doc_frac_chars_top_3gram": 0.0031751599162817,
"rps_doc_frac_chars_top_4gram": 0.005997530184686184,
"rps_doc_books_importance": -911.7395629882812,
"rps_doc_books_importance_length_correction": -911.7395629882812,
"rps_doc_openwebtext_importance": -406.26702880859375,
"rps_doc_openwebtext_importance_length_correction": -406.26702880859375,
"rps_doc_wikipedia_importance": -345.1173400878906,
"rps_doc_wikipedia_importance_length_correction": -345.1173400878906
},
"fasttext": {
"dclm": 0.5178614854812622,
"english": 0.9768500924110413,
"fineweb_edu_approx": 1.4046066999435425,
"eai_general_math": 0.22774887084960938,
"eai_open_web_math": 0.264898419380188,
"eai_web_code": 0.0475652813911438
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.072",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "363.25",
"labels": {
"level_1": "Social sciences",
"level_2": "Social service and Societies",
"level_3": "Political activists"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "5",
"label": "Evaluate"
},
"secondary": {
"code": "4",
"label": "Analyze"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "1",
"label": "News/Editorial"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "16",
"label": "Personal Blog"
},
"secondary": {
"code": "10",
"label": "Knowledge Article"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "6",
"label": "Not Applicable/Indeterminate"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "1",
"label": "General Audience"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
3,524,622,270,031,851,500
|
Se connecter
ou
Les différentes écritures d'un nombre
I
Les différentes écritures d'un nombre
A
L'écriture décimale
Écriture décimale
Tout nombre dont la partie décimale est finie admet une écriture décimale.
3,141592654 est une écriture décimale.
\(\displaystyle{\pi\approx3,141\ 592\ 654...}\) Ce n'est pas une écriture décimale car le nombre de chiffres après la virgule est infini.
• Il est possible d'ajouter un nombre infini de 0 après la dernière décimale sans changer la valeur du nombre. Par convention, l'écriture décimale d'un nombre s'arrête à la dernière décimale différente de 0.
• Dans cette convention, l'écriture décimale d'un entier ne présente pas de virgule.
\(\displaystyle{\dfrac{5}{2}}\) a pour écriture décimale : 2,5. Ce nombre est aussi égal à 2,50 ou 2,50000 par exemple.
4 est une écriture décimale. L'entier 4 vaut également : 4,0 ou 4,00, etc.
B
L'écriture fractionnaire
Écriture fractionnaire
Soient a et b deux nombres, avec b différent de 0.
L'écriture fractionnaire \(\displaystyle{\dfrac{a}{b}}\) représente le quotient de a par b. Lorsque a et b sont entiers, on dit que \(\displaystyle{\dfrac{a}{b}}\) est une fraction.
\(\displaystyle{17,1\div5,6}\) a pour écriture fractionnaire \(\displaystyle{\dfrac{17,1}{5,6}}\).
Attention le dénominateur est toujours différent de 0. La division par 0 n'existe pas.
Écriture fractionnaire
Tout nombre dont la partie décimale est finie ou périodique (répétition infinie d'une séquence de décimales) admet une écriture fractionnaire.
\(\displaystyle{0,107\ 107\ 107...=\dfrac{107}{999}}\)
\(\displaystyle{0,33\ 333\ 333...=\dfrac{1}{3}}\)
\(\displaystyle{0,454=\dfrac{454}{1\ 000}}\)
• Un nombre admettant une écriture fractionnaire en admet une infinité, ce qui signifie que plusieurs fractions peuvent être égales au même nombre.
• Un nombre admettant une écriture fractionnaire admet une écriture décimale dont la partie décimale est finie ou périodique.
2,45 admet pour écritures fractionnaires (entre autres) : \(\displaystyle{\dfrac{245}{100}}\), \(\displaystyle{\dfrac{49}{20}}\).
0,33333... admet pour écritures fractionnaires : \(\displaystyle{\dfrac{1}{3}}\), \(\displaystyle{\dfrac{6}{18}}\).
C
L'écriture scientifique
Tout nombre décimal non nul b admet une écriture de la forme suivante :
\(\displaystyle{a\times10^{p}}\)
avec p entier relatif, et :
• \(\displaystyle{1 \leq a \lt 10}\) si le nombre est positif
• \(\displaystyle{- 10 \lt a \leq -1}\) si le nombre est négatif.
Cette écriture est unique et s'appelle écriture scientifique du nombre b.
312,8 admet pour écriture scientifique : \(\displaystyle{3,128\times10^{2}}\).
−0,00056 admet pour écriture scientifique : \(\displaystyle{-5,6\times10^{-4}}\).
II
Quotients, puissances et racines carrées
A
Les quotients
Dans toutes les propriétés ci-dessous, a, b, c et d sont des nombres quelconques avec c et d non nuls.
\(\displaystyle{\dfrac{a}{c}=\dfrac{a \times d}{c \times d}}\)
On prend \(\displaystyle{d=3}\) :
\(\displaystyle{\dfrac{4}{7}=\dfrac{4\times3}{7\times3}=\dfrac{12}{21}}\)
\(\displaystyle{\dfrac{a}{c}+\dfrac{b}{c}=\dfrac{a + b}{c}}\)
\(\displaystyle{\dfrac{6}{17}+\dfrac{9}{17}=\dfrac{6+9}{17}=\dfrac{15}{17}}\)
\(\displaystyle{\dfrac{a}{c}-\dfrac{b}{c}=\dfrac{a - b}{c}}\)
\(\displaystyle{\dfrac83-\dfrac43=\dfrac{8-4}{3}=\dfrac{4}{3}}\)
\(\displaystyle{\dfrac{a}{c}\times \dfrac{b}{d}=\dfrac{a \times b}{c \times d}}\)
\(\displaystyle{\dfrac{2}{5}\times\dfrac{8}{7}=\dfrac{2\times8}{5\times7}=\dfrac{16}{35}}\)
Si, de plus, \(\displaystyle{b\neq0}\) :
\(\displaystyle{\dfrac{\dfrac{a}{b}}{\dfrac{c}{d}}=\dfrac{a}{b}\times \dfrac{d}{c}}\)
\(\displaystyle{\dfrac{\dfrac{2}{3}}{\dfrac{4}{5}}=\dfrac{2}{3}\times\dfrac{5}{4}=\dfrac{10}{12}=\dfrac{5}{6}}\)
Produit en croix :
Si \(\displaystyle{\dfrac{a}{c}=\dfrac{b}{d}}\), alors \(\displaystyle{ad = bc}\)
\(\displaystyle{\dfrac{57}{21}=\dfrac{19}{7}}\) équivaut à \(\displaystyle{57\times7=19\times21}\)
Produit en croix :
Soient a, b, c et d sont des nombres quelconques avec c et d non nuls.
Si \(\displaystyle{\dfrac{a}{c}=\dfrac{b}{d}}\), alors \(\displaystyle{a\times d=b\times c}\)
Dans un calcul comportant des quotients, le trait de fraction tient lieu de parenthèses. Ce qui signifie notamment que le signe présent devant un quotient se répercute sur l'ensemble des nombres du numérateur.
\(\displaystyle{\dfrac{51}{11}-\dfrac{21 - 142}{11}=\dfrac{51 - \left(21 - 142\right)}{11}=\dfrac{51 {\color{Red}-} 21 {\color{Red}+} 142}{11}}\)
B
Les puissances
Puissance
Soit n un entier positif non nul supérieur ou égal à 1. On désigne par \(\displaystyle{a^{n}}\) la puissance n du nombre a, telle que :
\(\displaystyle{a^n = \underbrace{a \times a \times ... \times a}_{n \text{ facteurs}}}\)
• L'entier n est appelé l'exposant.
• \(\displaystyle{a^{n}}\) se lit "a exposant n" ou "a puissance n".
• \(\displaystyle{a^{n}}\) est appelé puissance n-ième de a.
\(\displaystyle{2^5 = 2 \times 2 \times 2 \times 2 \times 2 = 32}\)
Soit a un nombre non nul :
\(\displaystyle{a^{0} = 1}\)
\(\displaystyle{13^0=1}\)
Soit n un entier positif et a un nombre non nul :
\(\displaystyle{\dfrac{1}{a^{n}}= a^{-n}}\)
\(\displaystyle{\dfrac{1}{4^{2}} = 4^{-2} }\)
\(\displaystyle{\dfrac{1}{4^{-3}} = 4^{3} }\)
Pour tout entier n :
\(\displaystyle{1^n=1}\)
Pour tout entier non nul n :
\(\displaystyle{0^n=0}\)
Soient a et b deux nombres relatifs non nuls, n et p deux entiers relatifs :
\(\displaystyle{a^{n} \times a^{p} = a^{n+p}}\)
\(\displaystyle{3^{8} \times 3^{-2} = 3^{8-2} = 3^6}\)
\(\displaystyle{\left(a^{n}\right)^{p} = a^{n\times p}}\)
\(\displaystyle{\left(5^{2}\right)^{4} = 5^{2 \times 4} = 5^8}\)
\(\displaystyle{\dfrac{a^{n}}{a^{p}}= a^{n-p}}\)
\(\displaystyle{\dfrac{4^{5}}{4^{3}} = 4^{5-3} = 4^2}\)
\(\displaystyle{\left(ab\right)^{n} = a^{n} \times b^{n}}\)
\(\displaystyle{\left(2\times5\right)^{3} = 2^{3} \times 5^{3}}\)
\(\displaystyle{\left(\dfrac{a}{b}\right)^{n}=\dfrac{a^{n}}{b^{n}}}\)
\(\displaystyle{\left(\dfrac{2}{3}\right)^{9} = \dfrac{2^{9}}{3^{9}}}\)
Soit a un nombre non nul. Alors \(\displaystyle{a^{-1}}\) est l'inverse de a.
C
Les racines carrées
Racine carrée
Soit a un nombre positif.
On appelle la racine carrée de a le nombre positif dont le carré est a. On le note \(\displaystyle{\sqrt{a}}\). On a :
\(\displaystyle{\left(\sqrt{a}\right)^{2} = a}\)
\(\displaystyle{\left( \sqrt{15} \right)^{2}=15}\)
Pour les racines carrées que l'on obtient pas directement à partir des tables de multiplication, c'est-à-dire les racines carrées des carrés parfaits, on utilise la calculatrice et la touche \(\displaystyle{\sqrt{}}\).
On obtient alors une valeur approchée du résultat dans la plupart des cas.
Carré parfait
On appelle carré parfait tout nombre égal au carré d'un entier.
Le tableau suivant donne les premiers carrés parfaits, c'est-à-dire les premiers carrés d'entiers naturels :
-
La racine carrée d'un carré parfait est donc un entier.
Soit a un nombre positif. On a :
\(\displaystyle{\sqrt{a^{2}} = a}\)
\(\displaystyle{\left(\sqrt{a}\right)^2 = a}\)
\(\displaystyle{\sqrt{16}=\sqrt{4^{2}}= 4}\)
Soit a un nombre négatif :
\(\displaystyle{\sqrt{a^{2}} = - a}\)
Par ailleurs, \(\displaystyle{\left(\sqrt{a}\right)^2}\) n'existe pas car \(\displaystyle{\sqrt{a}}\) n'existe pas.
\(\displaystyle{\sqrt{\left(- 5\right)^{2}}=\sqrt{25}=\sqrt{5^{2}}= 5}\)
Avec :
\(\displaystyle{5=-\left(-5\right)}\)
III
Les règles générales de calcul
A
Les priorités entre les opérations
Priorités des opérations
Dans une suite de calculs, on effectue dans l'ordre :
• Les calculs entre parenthèses
• Les puissances
• Les multiplications et les divisions
• Les additions et les soustractions
\(\displaystyle{A=13-15\times \underbrace{\left(81\div9-3^2\right)}_{\text{Parenthèse}}-8}\)
\(\displaystyle{A=13-15\times\left(81\div9-\underbrace{3^2}_{\text{1er calcul}}\right)-8}\)
\(\displaystyle{A=13-15\times\left(\underbrace{81\div9}_{\text{2e calcul}}-9\right)-8}\)
\(\displaystyle{A=13-15\times\left(\underbrace{9-9}_{\text{3e calcul}}\right)-8}\)
\(\displaystyle{A=13-\underbrace{15\times0}_{\text{4e calcul}}-8}\)
\(\displaystyle{A=13-0-8}\)
\(\displaystyle{A=13-8}\)
\(\displaystyle{A=5}\)
B
L'opposé d'un nombre
Opposé d'un nombre
Soit a un nombre quelconque. On appelle opposé de a le nombre \(\displaystyle{-a}\).
L'opposé du nombre 78 est −78.
• Si a est un nombre positif, son opposé est négatif.
• Si a est un nombre négatif, son opposé est positif.
L'opposé de (+56) est (−56).
L'opposé de (−8,1) est (+8,1).
Pour tout nombre a, on a :
\(\displaystyle{a + \left(- a\right) = \left(-a\right) + a = 0}\)
On remarque que \(\displaystyle{\left(−8,1\right) + \left(+8,1\right) = 0}\).
Soustraire un nombre, c'est ajouter son opposé.
\(\displaystyle{5,65 − 9,6 = 5,65 + \left(−9,6\right) = −3,95}\)
\(\displaystyle{17y − \left(−4x\right) = 17y + \left(+4x\right) = 17y + 4x}\)
Quand il y a un signe "-" devant une parenthèse, on peut supprimer les parenthèses et le signe "-", en réécrivant les termes de la parenthèse en changeant leurs signes.
\(\displaystyle{-\left( a+2 \right)=-a-2}\)
C
L'inverse d'un nombre
Inverse d'un nombre
Soit a un nombre non nul. L'inverse de a est le nombre qui, multiplié par a, donne 1.
\(\displaystyle{100\times0,01=1}\)
Ainsi, l'inverse de 100 est 0,01.
Si a est un nombre non nul, l'inverse de a est égal à :
\(\displaystyle{\dfrac{1}{a}}\)
L'inverse de 5 est \(\displaystyle{\dfrac15=0,2}\).
L'inverse de −2 est \(\displaystyle{\dfrac{1}{-2}=-\dfrac{1}{2}=-0,5}\).
Soient a et b deux nombres non nuls. L'inverse de \(\displaystyle{\dfrac{a}{b}}\) est \(\displaystyle{\dfrac{b}{a}}\).
L'inverse de \(\displaystyle{\dfrac{17}{31}}\) est \(\displaystyle{\dfrac{31}{17}}\).
L'inverse de \(\displaystyle{\dfrac{-7}{6}}\) est \(\displaystyle{\dfrac{-6}{7}}\).
L'inverse de \(\displaystyle{\dfrac{1}{12}}\) est \(\displaystyle{\dfrac{12}{1}=12}\).
Diviser par un nombre non nul, c'est multiplier par son inverse. Soient a et b deux nombres non nuls, alors :
• Diviser par a c'est multiplier par \(\displaystyle{\dfrac{1}{a}}\).
• Diviser par \(\displaystyle{\dfrac{1}{a}}\) c'est multiplier par \(\displaystyle{a}\).
• Diviser par \(\displaystyle{\dfrac{a}{b}}\) c'est multiplier par \(\displaystyle{\dfrac{b}{a}}\).
\(\displaystyle{125\div25=125\times\dfrac{1}{25}=125\times0,04=5}\)
\(\displaystyle{12\div\dfrac14=12\times4=48}\)
\(\displaystyle{18\div\dfrac{9}{2}=18\times \dfrac29=\dfrac{36}{9}=4}\)
|
{
"url": "https://www.kartable.fr/ressources/mathematiques/cours/les-differentes-ecritures-d-un-nombre",
"source_domain": "www.kartable.fr",
"snapshot_id": "crawl=CC-MAIN-2017-34",
"warc_metadata": {
"Content-Length": "275950",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:Z5NFQUTEJORQZ7T5NNJEZPTAJ45TGVYX",
"WARC-Concurrent-To": "<urn:uuid:babc1436-1713-46bf-b0e6-461d0ac0af99>",
"WARC-Date": "2017-08-23T00:51:48Z",
"WARC-IP-Address": "52.50.62.254",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:B5BLCGTFTVGMQGMWKOAR4FZKFN5YGPHI",
"WARC-Record-ID": "<urn:uuid:d5465c8f-80dc-426d-8407-83c83d904dc6>",
"WARC-Target-URI": "https://www.kartable.fr/ressources/mathematiques/cours/les-differentes-ecritures-d-un-nombre",
"WARC-Truncated": "length",
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:dc1d78d8-0db5-489c-91fe-2bf13cf9a3d5>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-164-5-165.ec2.internal\r\nsoftware: Nutch 1.6 (CC)\r\nisPartOf: CC-MAIN-2017-34\r\noperator: Common Crawl Admin\r\ndescription: Wide crawl of the web for August 2017\r\npublisher: Common Crawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
13,
16,
17,
55,
56,
58,
59,
97,
98,
100,
101,
121,
122,
140,
141,
216,
217,
256,
257,
395,
396,
606,
693,
694,
814,
815,
890,
891,
893,
894,
919,
920,
943,
944,
995,
1177,
1178,
1277,
1278,
1365,
1366,
1389,
1390,
1533,
1534,
1589,
1590,
1640,
1641,
1686,
1687,
1837,
1965,
1966,
2096,
2097,
2213,
2214,
2216,
2217,
2241,
2242,
2314,
2315,
2348,
2349,
2377,
2378,
2442,
2510,
2511,
2585,
2586,
2665,
2666,
2748,
2749,
2752,
2753,
2794,
2795,
2797,
2798,
2812,
2813,
2916,
2917,
2980,
2981,
3015,
3016,
3090,
3091,
3153,
3154,
3232,
3233,
3295,
3296,
3361,
3362,
3444,
3445,
3537,
3538,
3579,
3580,
3666,
3667,
3780,
3781,
3800,
3801,
3883,
3884,
3983,
3984,
4003,
4004,
4075,
4076,
4170,
4171,
4381,
4382,
4528,
4530,
4531,
4546,
4547,
4557,
4558,
4694,
4695,
4785,
4786,
4824,
4895,
4958,
4959,
5027,
5028,
5055,
5056,
5085,
5086,
5112,
5113,
5163,
5164,
5208,
5209,
5255,
5256,
5302,
5303,
5324,
5325,
5350,
5351,
5380,
5381,
5406,
5407,
5484,
5485,
5533,
5534,
5589,
5590,
5648,
5649,
5714,
5715,
5764,
5765,
5821,
5822,
5882,
5883,
5949,
5950,
6020,
6021,
6093,
6094,
6172,
6173,
6175,
6176,
6196,
6197,
6211,
6212,
6238,
6357,
6358,
6407,
6408,
6459,
6460,
6679,
6754,
6755,
6769,
6770,
6834,
6835,
6944,
6945,
6947,
6948,
7004,
7005,
7038,
7039,
7075,
7076,
7123,
7124,
7169,
7170,
7197,
7198,
7236,
7237,
7353,
7354,
7427,
7428,
7435,
7436,
7474,
7475,
7479,
7480,
7511,
7512,
7514,
7515,
7550,
7551,
7576,
7577,
7631,
7632,
7666,
7685,
7726,
7765,
7766,
7859,
7860,
7952,
7953,
8042,
8043,
8126,
8127,
8195,
8196,
8224,
8225,
8251,
8252,
8275,
8276,
8278,
8279,
8300,
8301,
8320,
8321,
8406,
8407,
8438,
8439,
8495,
8551,
8552,
8581,
8582,
8613,
8614,
8641,
8642,
8708,
8709,
8787,
8788,
8836,
8837,
8902,
8903,
8981,
8982,
9151,
9152,
9196,
9197,
9199,
9200,
9222,
9223,
9243,
9244,
9330,
9331,
9366,
9367,
9401,
9402,
9458,
9459,
9491,
9492,
9544,
9545,
9618,
9619,
9738,
9739,
9825,
9826,
9910,
9911,
9998,
9999,
10109,
10110,
10182,
10273,
10375,
10376,
10444,
10445,
10492,
10493
],
"line_end_idx": [
13,
16,
17,
55,
56,
58,
59,
97,
98,
100,
101,
121,
122,
140,
141,
216,
217,
256,
257,
395,
396,
606,
693,
694,
814,
815,
890,
891,
893,
894,
919,
920,
943,
944,
995,
1177,
1178,
1277,
1278,
1365,
1366,
1389,
1390,
1533,
1534,
1589,
1590,
1640,
1641,
1686,
1687,
1837,
1965,
1966,
2096,
2097,
2213,
2214,
2216,
2217,
2241,
2242,
2314,
2315,
2348,
2349,
2377,
2378,
2442,
2510,
2511,
2585,
2586,
2665,
2666,
2748,
2749,
2752,
2753,
2794,
2795,
2797,
2798,
2812,
2813,
2916,
2917,
2980,
2981,
3015,
3016,
3090,
3091,
3153,
3154,
3232,
3233,
3295,
3296,
3361,
3362,
3444,
3445,
3537,
3538,
3579,
3580,
3666,
3667,
3780,
3781,
3800,
3801,
3883,
3884,
3983,
3984,
4003,
4004,
4075,
4076,
4170,
4171,
4381,
4382,
4528,
4530,
4531,
4546,
4547,
4557,
4558,
4694,
4695,
4785,
4786,
4824,
4895,
4958,
4959,
5027,
5028,
5055,
5056,
5085,
5086,
5112,
5113,
5163,
5164,
5208,
5209,
5255,
5256,
5302,
5303,
5324,
5325,
5350,
5351,
5380,
5381,
5406,
5407,
5484,
5485,
5533,
5534,
5589,
5590,
5648,
5649,
5714,
5715,
5764,
5765,
5821,
5822,
5882,
5883,
5949,
5950,
6020,
6021,
6093,
6094,
6172,
6173,
6175,
6176,
6196,
6197,
6211,
6212,
6238,
6357,
6358,
6407,
6408,
6459,
6460,
6679,
6754,
6755,
6769,
6770,
6834,
6835,
6944,
6945,
6947,
6948,
7004,
7005,
7038,
7039,
7075,
7076,
7123,
7124,
7169,
7170,
7197,
7198,
7236,
7237,
7353,
7354,
7427,
7428,
7435,
7436,
7474,
7475,
7479,
7480,
7511,
7512,
7514,
7515,
7550,
7551,
7576,
7577,
7631,
7632,
7666,
7685,
7726,
7765,
7766,
7859,
7860,
7952,
7953,
8042,
8043,
8126,
8127,
8195,
8196,
8224,
8225,
8251,
8252,
8275,
8276,
8278,
8279,
8300,
8301,
8320,
8321,
8406,
8407,
8438,
8439,
8495,
8551,
8552,
8581,
8582,
8613,
8614,
8641,
8642,
8708,
8709,
8787,
8788,
8836,
8837,
8902,
8903,
8981,
8982,
9151,
9152,
9196,
9197,
9199,
9200,
9222,
9223,
9243,
9244,
9330,
9331,
9366,
9367,
9401,
9402,
9458,
9459,
9491,
9492,
9544,
9545,
9618,
9619,
9738,
9739,
9825,
9826,
9910,
9911,
9998,
9999,
10109,
10110,
10182,
10273,
10375,
10376,
10444,
10445,
10492,
10493,
10564
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 10564,
"ccnet_original_nlines": 338,
"rps_doc_curly_bracket": 0.0683453232049942,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.12036073952913284,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.01318071037530899,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.5143947005271912,
"rps_doc_frac_unique_words": 0.3586083948612213,
"rps_doc_mean_word_length": 6.495985507965088,
"rps_doc_num_sentences": 74,
"rps_doc_symbol_to_word_ratio": 0.0017343000508844852,
"rps_doc_unigram_entropy": 5.306118965148926,
"rps_doc_word_count": 1121,
"rps_doc_frac_chars_dupe_10grams": 0.01263388991355896,
"rps_doc_frac_chars_dupe_5grams": 0.10532820969820023,
"rps_doc_frac_chars_dupe_6grams": 0.0876132920384407,
"rps_doc_frac_chars_dupe_7grams": 0.061521559953689575,
"rps_doc_frac_chars_dupe_8grams": 0.046278491616249084,
"rps_doc_frac_chars_dupe_9grams": 0.01263388991355896,
"rps_doc_frac_chars_top_2gram": 0.01757759042084217,
"rps_doc_frac_chars_top_3gram": 0.009887389838695526,
"rps_doc_frac_chars_top_4gram": 0.012496570125222206,
"rps_doc_books_importance": -988.621337890625,
"rps_doc_books_importance_length_correction": -988.621337890625,
"rps_doc_openwebtext_importance": -559.337158203125,
"rps_doc_openwebtext_importance_length_correction": -559.337158203125,
"rps_doc_wikipedia_importance": -500.1654357910156,
"rps_doc_wikipedia_importance_length_correction": -500.1654357910156
},
"fasttext": {
"dclm": 0.9079033732414246,
"english": 0.027524640783667564,
"fineweb_edu_approx": 1.6127915382385254,
"eai_general_math": 0.4370289444923401,
"eai_open_web_math": 0.9885489344596863,
"eai_web_code": 0.9247467517852783
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "513.01",
"labels": {
"level_1": "Science and Natural history",
"level_2": "Mathematics",
"level_3": "Geometry"
}
},
"secondary": {
"code": "512.01",
"labels": {
"level_1": "Science and Natural history",
"level_2": "Mathematics",
"level_3": "Algebra"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "0",
"label": "No missing content"
}
},
"document_type_v2": {
"primary": {
"code": "23",
"label": "Tutorial"
},
"secondary": {
"code": "10",
"label": "Knowledge Article"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "1",
"label": "General Audience"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-487,170,526,679,724,860
|
Index: test/tests/typedObjects.js =================================================================== --- a/test/tests/typedObjects.js +++ b/test/tests/typedObjects.js @@ -674,9 +674,85 @@ array5.release(); array5 = uint32Array(9); equal(array5.arrayBufferIndex, 5, "Buffer indexes for large arrays aren't reused"); equal(array5.arrayByteOffset, 0, "Large array is allocated at zero offset"); for (let array of [array1, array2, array3, array4, array5]) array.release(); }); + + test("String type", function() + { + let {string} = require("typedObjects"); + + let s1 = string(); + ok(s1, "String created without parameters"); + equal(s1.length, 0, "String length is zero"); + equal(s1.toString(), "", "JavaScript representation is empty string"); + s1.release(); + + let s2 = string(4); + ok(s2, "String with particular length created"); + equal(s2.length, 4, "String length set correctly"); + for (let i = 0; i < s2.length; i++) + s2.set(i, i + 0xF000); + equal(s2.toString(), "\uF000\uF001\uF002\uF003", "JavaScript representation is correct"); + s2.release(); + + let s3 = string("test"); + ok(s3, "String created from JS string"); + equal(s3.length, 4, "String length set correctly"); + equal(s3.get(2), "s".charCodeAt(0), "Array items represent string letters"); + equal(s3.toString(), "test", "JavaScript representation is correct"); + s3.release(); + + let s4 = string("somelongstring", 2, 6); + ok(s4, "String created as JS substring"); + equal(s4.length, 6, "String length set correctly"); + equal(s4.toString(), "melong", "JavaScript representation is correct"); + s4.release(); + + let s5 = string("abc", 2, 6); + ok(s5, "String created as JS substring with excessive length parameter"); + equal(s5.length, 1, "String length set correctly"); + equal(s5.toString(), "c", "JavaScript representation is correct"); + s5.release(); + + let s6 = string("abc", 8, 1); + ok(s6, "String created as JS substring with too large offset parameter"); + equal(s6.length, 0, "String length set correctly"); + equal(s6.toString(), "", "JavaScript representation is correct"); + s6.release(); + + let s7 = string("abc", 1); + ok(s7, "String created as JS substring without length parameter"); + equal(s7.length, 2, "String length set correctly"); + equal(s7.toString(), "bc", "JavaScript representation is correct"); + s7.release(); + + let s8 = string("somelongstring"); + let s9 = string(s8, 2, 6); + ok(s9, "String created as typed substring"); + equal(s9.length, 6, "String length set correctly"); + equal(s9.toString(), "melong", "JavaScript representation is correct"); + s9.release(); + + let s10 = string(s8, 4, 20); + ok(s10, "String created as typed substring with excessive length parameter"); + equal(s10.length, 10, "String length set correctly"); + equal(s10.toString(), "longstring", "JavaScript representation is correct"); + s10.release(); + + let s11 = string(s8, 20, 1); + ok(s11, "String created as typed substring with too large offset parameter"); + equal(s11.length, 0, "String length set correctly"); + equal(s11.toString(), "", "JavaScript representation is correct"); + s11.release(); + + let s12 = string(s8, 4); + ok(s12, "String created as typed substring without length parameter"); + equal(s12.length, 10, "String length set correctly"); + equal(s12.toString(), "longstring", "JavaScript representation is correct"); + s12.release(); + s8.release(); + }); })();
|
{
"url": "https://codereview.adblockplus.org/download/issue5665229014827008_5178081291534336_6038809917521920.diff",
"source_domain": "codereview.adblockplus.org",
"snapshot_id": "CC-MAIN-2024-22",
"warc_metadata": {
"Content-Length": "4422",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:K5IHGFQB4CGJ5JFGBSAI77DAJDMBLPWN",
"WARC-Concurrent-To": "<urn:uuid:7b614dac-ffe8-4e08-afac-550e3f29aa6f>",
"WARC-Date": "2024-05-21T18:53:04Z",
"WARC-IP-Address": "34.36.36.136",
"WARC-Identified-Payload-Type": "text/x-diff",
"WARC-Payload-Digest": "sha1:X6FREFXWKX52DFBJNPTF27SUHZI4XB65",
"WARC-Record-ID": "<urn:uuid:555ad9f5-b9e7-48f8-9c8e-8c564b715f23>",
"WARC-Target-URI": "https://codereview.adblockplus.org/download/issue5665229014827008_5178081291534336_6038809917521920.diff",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:788cd03a-ebea-4b8e-9e47-36b586b9d9ea>"
},
"warc_info": "isPartOf: CC-MAIN-2024-22\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for May 2024\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-21\r\nsoftware: Apache Nutch 1.19 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.5-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0
],
"line_end_idx": [
3384
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 3384,
"ccnet_original_nlines": 0,
"rps_doc_curly_bracket": 0.0017730500549077988,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.08840412646532059,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.005740529857575893,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.5212399363517761,
"rps_doc_frac_unique_words": 0.4164222776889801,
"rps_doc_mean_word_length": 6.642228603363037,
"rps_doc_num_sentences": 46,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.367059230804443,
"rps_doc_word_count": 341,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.30728477239608765,
"rps_doc_frac_chars_dupe_6grams": 0.07593818753957748,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.058278150856494904,
"rps_doc_frac_chars_top_3gram": 0.12626932561397552,
"rps_doc_frac_chars_top_4gram": 0.10596025735139847,
"rps_doc_books_importance": -338.24517822265625,
"rps_doc_books_importance_length_correction": -338.24517822265625,
"rps_doc_openwebtext_importance": -128.6621551513672,
"rps_doc_openwebtext_importance_length_correction": -128.6621551513672,
"rps_doc_wikipedia_importance": -21.23826026916504,
"rps_doc_wikipedia_importance_length_correction": -21.23826026916504
},
"fasttext": {
"dclm": 0.9999455213546753,
"english": 0.4897291958332062,
"fineweb_edu_approx": 1.5134292840957642,
"eai_general_math": 0.9889953136444092,
"eai_open_web_math": 0.6470944881439209,
"eai_web_code": 0.6227796673774719
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.133",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "4",
"label": "Code/Software"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "0",
"label": "No missing content"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "21",
"label": "Customer Support"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "4",
"label": "Graduate/Expert Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
7,691,145,173,395,964,000
|
Java:String和Date、Timestamp之间的转换
经常在java编程中遇到时间转换的问题。其实这个问题不大的,java本身就有提供SimpleDateFormat 类。但是之前一般不会去记它,通常是遇到了这个问题再Google或百度一下,因为网上对于这个小问题是有很多资源的,所以也就很好解决了。但是今天却觉得,应该“记一记”,所以索性写这篇博客。因为网上资源多,在自己理解的基础上就不原创,而是转载了一篇自己觉得还不错的文章过来。在这里附上原文地址
以下为正文部分:
一、String与Date(java.util.Date)互转
1.1 String -> Date
Java代码 收藏代码
String dateStr = “2010/05/04 12:34:23”;
Date date = new Date();
//注意format的格式要与日期String的格式相匹配
DateFormat sdf = new SimpleDateFormat(“yyyy/MM/dd HH:mm:ss”);
try {
date = sdf.parse(dateStr);
System.out.println(date.toString());
} catch (Exception e) {
e.printStackTrace();
}
1.2 Date -> String
日期向字符串转换,可以设置任意的转换格式format
Java代码 收藏代码
String dateStr = “”;
Date date = new Date();
//format的格式可以任意
DateFormat sdf = new SimpleDateFormat(“yyyy/MM/dd HH:mm:ss”);
DateFormat sdf2 = new SimpleDateFormat(“yyyy-MM-dd HH/mm/ss”);
try {
dateStr = sdf.format(date);
System.out.println(dateStr);
dateStr = sdf2.format(date);
System.out.println(dateStr);
} catch (Exception e) {
e.printStackTrace();
}
二、String与Timestamp互转
2.1 String ->Timestamp
使用Timestamp的valueOf()方法
Java代码 收藏代码
Timestamp ts = new Timestamp(System.currentTimeMillis());
String tsStr = “2011-05-09 11:49:45”;
try {
ts = Timestamp.valueOf(tsStr);
System.out.println(ts);
} catch (Exception e) {
e.printStackTrace();
}
注:String的类型必须形如: yyyy-mm-dd hh:mm:ss[.f…] 这样的格式,中括号表示可选,否则报错!!!
如果String为其他格式,可考虑重新解析下字符串,再重组~~
2.2 Timestamp -> String
使用Timestamp的toString()方法或者借用DateFormat
Java代码 收藏代码
Timestamp ts = new Timestamp(System.currentTimeMillis());
String tsStr = “”;
DateFormat sdf = new SimpleDateFormat(“yyyy/MM/dd HH:mm:ss”);
try {
//方法一
tsStr = sdf.format(ts);
System.out.println(tsStr);
//方法二
tsStr = ts.toString();
System.out.println(tsStr);
} catch (Exception e) {
e.printStackTrace();
}
很容易能够看出来,方法一的优势在于可以灵活的设置字符串的形式。
三、Date( java.util.Date )和Timestamp互转
声明:查API可知,Date和Timesta是父子类关系
3.1 Timestamp -> Date
Java代码 收藏代码
Timestamp ts = new Timestamp(System.currentTimeMillis());
Date date = new Date();
try {
date = ts;
System.out.println(date);
} catch (Exception e) {
e.printStackTrace();
}
很简单,但是此刻date对象指向的实体却是一个Timestamp,即date拥有Date类的方法,但被覆盖的方法的执行实体在Timestamp中。
3.2 Date -> Timestamp
父类不能直接向子类转化,可借助中间的String~~~~
注:使用以下方式更简洁
Timestamp ts = new Timestamp(date.getTime());
希望对大家有所帮助
相关文章
相关标签/搜索
|
{
"url": "http://www.voidcn.com/article/p-bwpuyrxr-tk.html",
"source_domain": "www.voidcn.com",
"snapshot_id": "crawl=CC-MAIN-2017-47",
"warc_metadata": {
"Content-Length": "32021",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:YR2WOPPBAV2MPPNBYLXTF52PACCLBATI",
"WARC-Concurrent-To": "<urn:uuid:1c70d8ba-635e-418a-9b66-19b7007e490c>",
"WARC-Date": "2017-11-24T13:13:23Z",
"WARC-IP-Address": "47.92.138.19",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:QWTG3ZPKTA77GZNU4JT6IPWS3OUURFDP",
"WARC-Record-ID": "<urn:uuid:50b13200-25d2-42e6-bb52-8ac1f7a56cba>",
"WARC-Target-URI": "http://www.voidcn.com/article/p-bwpuyrxr-tk.html",
"WARC-Truncated": "length",
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:7c310e23-c5b8-4aa1-b8e8-e5f203154a0e>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-164-5-214.ec2.internal\r\nsoftware: Nutch 1.6 (CC)\r\nisPartOf: CC-MAIN-2017-47\r\noperator: Common Crawl Admin\r\ndescription: Wide crawl of the web for November 2017\r\npublisher: Common Crawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
32,
33,
234,
235,
244,
245,
277,
278,
297,
298,
310,
350,
374,
404,
466,
472,
499,
536,
560,
581,
583,
584,
603,
604,
631,
643,
664,
688,
704,
766,
829,
835,
863,
892,
921,
950,
974,
995,
997,
998,
1019,
1020,
1043,
1044,
1068,
1080,
1138,
1176,
1182,
1213,
1237,
1261,
1282,
1284,
1348,
1380,
1381,
1405,
1406,
1445,
1446,
1458,
1516,
1535,
1597,
1603,
1609,
1633,
1660,
1666,
1689,
1716,
1740,
1761,
1763,
1795,
1796,
1833,
1834,
1863,
1864,
1886,
1887,
1899,
1957,
1981,
1987,
1998,
2024,
2048,
2069,
2071,
2145,
2146,
2168,
2169,
2198,
2210,
2256,
2257,
2267,
2268,
2273,
2274
],
"line_end_idx": [
32,
33,
234,
235,
244,
245,
277,
278,
297,
298,
310,
350,
374,
404,
466,
472,
499,
536,
560,
581,
583,
584,
603,
604,
631,
643,
664,
688,
704,
766,
829,
835,
863,
892,
921,
950,
974,
995,
997,
998,
1019,
1020,
1043,
1044,
1068,
1080,
1138,
1176,
1182,
1213,
1237,
1261,
1282,
1284,
1348,
1380,
1381,
1405,
1406,
1445,
1446,
1458,
1516,
1535,
1597,
1603,
1609,
1633,
1660,
1666,
1689,
1716,
1740,
1761,
1763,
1795,
1796,
1833,
1834,
1863,
1864,
1886,
1887,
1899,
1957,
1981,
1987,
1998,
2024,
2048,
2069,
2071,
2145,
2146,
2168,
2169,
2198,
2210,
2256,
2257,
2267,
2268,
2273,
2274,
2281
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 2281,
"ccnet_original_nlines": 104,
"rps_doc_curly_bracket": 0.008768079802393913,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.06476189941167831,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.01714286021888256,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.5771428346633911,
"rps_doc_frac_unique_words": 0.4363636374473572,
"rps_doc_mean_word_length": 10.86060619354248,
"rps_doc_num_sentences": 42,
"rps_doc_symbol_to_word_ratio": 0.0019047600217163563,
"rps_doc_unigram_entropy": 3.8585152626037598,
"rps_doc_word_count": 165,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.1897321343421936,
"rps_doc_frac_chars_dupe_6grams": 0.1629464328289032,
"rps_doc_frac_chars_dupe_7grams": 0.074776791036129,
"rps_doc_frac_chars_dupe_8grams": 0.074776791036129,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.02790178917348385,
"rps_doc_frac_chars_top_3gram": 0.0418526791036129,
"rps_doc_frac_chars_top_4gram": 0.086495541036129,
"rps_doc_books_importance": -270.0761413574219,
"rps_doc_books_importance_length_correction": -270.0761413574219,
"rps_doc_openwebtext_importance": -159.02452087402344,
"rps_doc_openwebtext_importance_length_correction": -159.02452087402344,
"rps_doc_wikipedia_importance": -55.02892303466797,
"rps_doc_wikipedia_importance_length_correction": -55.02892303466797
},
"fasttext": {
"dclm": 0.9455097317695618,
"english": 0.054928869009017944,
"fineweb_edu_approx": 3.308567523956299,
"eai_general_math": 0.003920199815183878,
"eai_open_web_math": 0.029291629791259766,
"eai_web_code": 0.9660034775733948
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1332",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.133",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "23",
"label": "Tutorial"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-9,058,457,064,584,071,000
|
Code: ListML
I’m sure the name has been used before, but I’m going to call this project ListML, standing for List Markup Language. It came about because I realized I write a lot of lists, almost always hierarchical, and then quite often I’d like to get those lists in HTML format. Normally I just write my lists in plain text, using tabs to indent things, and a few other minimal standards of markup, so I figured it couldn’t be that hard to write something to convert the plain text into HTML.
A little tinkering later and we have a basic set of formatting rules and a quick PHP script to convert plain text, hierarchical lists, into beautiful POSH + CSS. You can download the ListML script now, and then take that as a core parser to convert TXT to HTML, given the rules below.
Download ListML 1.1 (3.4 KiB, 1,118 hits)
As an example, here is a source TXT file, and the resulting HTML output.
The formatting rules are as follows:
1. Each line in your text file is a line item in your list
2. Indent by one tab-stop (NOT spaces) to create an indented list underneath the previous item
3. Put a “= ” (equals sign, followed by a space) at the start of a far-left-aligned line to create an H1 tag in your output
4. Put more equals signs to create smaller headings (== is a H2, === is a H3, etc)
5. Skip a line to put a HR
6. Links (http://…) will be converted to live hyperlinks
7. A line starting and ending with “#” will be “highlighted”
8. A line starting and ending with “-” will be crossed out/struck through
9. A line starting and ending with “`” (backtick) will be wrapped in <code> tags
10. The first Hx tag created will be used as the page <title>
11. All lists created will be OL (ordered lists) with default CSS attached. Feel free to change the CSS or use your list output elsewhere
You can consider this licensed under a GPL license.
How To Use
To use this specific ListML script, you need a host capable of running PHP.
1. Drop listml.php (from the download archive) into a directory on your server/host
2. Drop a correctly-formatted TXT file into the same directory, let’s call it “mylist.txt”
3. Request the listml.php file via a browser, with the base of the filename as the “file” parameter, which will look something like this: http://myserver/listml.php?file=mylist
4. Bask in the glory of your HTML list.
Obviously you could pull out the core of the parsing “engine” for ListML and use it in other places, but I’ll let you handle that.
What do you think?
|
{
"url": "https://dentedreality.com.au/projects/listml/",
"source_domain": "dentedreality.com.au",
"snapshot_id": "crawl=CC-MAIN-2017-47",
"warc_metadata": {
"Content-Length": "36226",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:ZEGW6YNPQBUKQ4CRVBTONZL32H4IWQII",
"WARC-Concurrent-To": "<urn:uuid:a283d50a-7422-4b96-8b6c-b333d87e801e>",
"WARC-Date": "2017-11-23T07:31:21Z",
"WARC-IP-Address": "205.186.137.169",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:NTK3NDIDR4RKLRNOLBOJMUPUSGMYMUPV",
"WARC-Record-ID": "<urn:uuid:2450b4ee-5f68-42e5-b95f-90006c465b82>",
"WARC-Target-URI": "https://dentedreality.com.au/projects/listml/",
"WARC-Truncated": "length",
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:1cb56e0e-5c26-4bb4-ba97-5f89f124b159>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-153-208-235.ec2.internal\r\nsoftware: Nutch 1.6 (CC)\r\nisPartOf: CC-MAIN-2017-47\r\noperator: Common Crawl Admin\r\ndescription: Wide crawl of the web for November 2017\r\npublisher: Common Crawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
13,
14,
496,
497,
782,
783,
827,
828,
901,
902,
939,
940,
1001,
1098,
1224,
1309,
1338,
1397,
1460,
1536,
1619,
1683,
1823,
1824,
1876,
1877,
1888,
1889,
1965,
1966,
2052,
2145,
2324,
2366,
2367,
2498,
2499
],
"line_end_idx": [
13,
14,
496,
497,
782,
783,
827,
828,
901,
902,
939,
940,
1001,
1098,
1224,
1309,
1338,
1397,
1460,
1536,
1619,
1683,
1823,
1824,
1876,
1877,
1888,
1889,
1965,
1966,
2052,
2145,
2324,
2366,
2367,
2498,
2499,
2517
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 2517,
"ccnet_original_nlines": 37,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.37068966031074524,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.056896548718214035,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.2258620709180832,
"rps_doc_frac_unique_words": 0.5154867172241211,
"rps_doc_mean_word_length": 4.236725807189941,
"rps_doc_num_sentences": 34,
"rps_doc_symbol_to_word_ratio": 0.0034482800401747227,
"rps_doc_unigram_entropy": 5.035301685333252,
"rps_doc_word_count": 452,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.05013054981827736,
"rps_doc_frac_chars_dupe_6grams": 0.05013054981827736,
"rps_doc_frac_chars_dupe_7grams": 0.05013054981827736,
"rps_doc_frac_chars_dupe_8grams": 0.0355091392993927,
"rps_doc_frac_chars_dupe_9grams": 0.0355091392993927,
"rps_doc_frac_chars_top_2gram": 0.018798960372805595,
"rps_doc_frac_chars_top_3gram": 0.02036553993821144,
"rps_doc_frac_chars_top_4gram": 0.025065269321203232,
"rps_doc_books_importance": -249.6850128173828,
"rps_doc_books_importance_length_correction": -249.6850128173828,
"rps_doc_openwebtext_importance": -134.9907989501953,
"rps_doc_openwebtext_importance_length_correction": -134.9907989501953,
"rps_doc_wikipedia_importance": -69.7636947631836,
"rps_doc_wikipedia_importance_length_correction": -69.7636947631836
},
"fasttext": {
"dclm": 0.11656486988067627,
"english": 0.8670142889022827,
"fineweb_edu_approx": 1.7688144445419312,
"eai_general_math": 0.9147064685821533,
"eai_open_web_math": 0.5640231370925903,
"eai_web_code": 0.1959100365638733
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.7",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "4",
"label": "Code/Software"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "23",
"label": "Tutorial"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "1",
"label": "No Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "6",
"label": "Not Applicable/Indeterminate"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "1",
"label": "General Audience"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
1,220,573,764,845,386,200
|
OSX/Lamadai.A: The Mac Payload
Earlier this month, researchers from AlienVault and Intego reported a new malware attack targeting Tibetan NGOs (Non-Governmental Organizations). The attack consisted of luring the victim into visiting a malicious website, which then would drop a malicious payload on the target’s computer using Java vulnerability CVE-2011-3544 and execute it. The webserver would serve a platform-specific JAR (Java Archive) dropper based on the browser’s UserAgent String to infect the user’s Windows or OS X system.
The OS X-specific dropper is also served to Linux clients. Since the dropped payload is designed for OS X only, Linux clients will not be infected.
This analysis is focused on the OS X payload and the network protocol it used to communicate with its Command and Control (C&C) server.
OS X uses the Mach-O file format for its executable files. For OSX/Lamadai.A, the Mach-O executable was compiled for 64-bit only, which is unusual since Mach-O binaries normally contain both the 32-bit and 64-bit versions of the executable.
Upon execution, the threat copies itself to /Library/Audio/Plug-Ins/AudioServer and adds a launcher script named ~/Library/LaunchAgents /com.apple.DockActions.plist pointing to the copied file to ensure it is executed whenever the current user logs in.
Note that by default, on OS X 10.7.2, regular users do not have write permissions to /Library/Audio/Plug-Ins/AudioServer, meaning this threat is not persistent (i.e. it won’t survive a reboot). We are unsure if older versions of OS X have different filesystem permissions. Nonetheless, using another location under the user’s home directory would have worked better for the attacker.
Afterwards, the threat will try to contact its C&C server by resolving dns.assyra.com (100.42.217.73 at the time of analysis, the domain now points to 127.0.0.1) and establishing a TCP connection to port 8008. The server will respond with a TCP RST unless it has some instructions to communicate. The infected system then falls into a busy wait loop, trying to reconnect at random intervals ranging from 0 to 10 seconds.
The server may issue one of the three following instructions to the infected system:
1. Upload a file: the C&C sends the path to upload, the client responds with the file content;
2. Download a file: the C&C sends the file path and content, the client creates the file with permissions set to 777 (-rwxrwxrwx);
3. Start a remote shell: the C&C sends an arbitrary shell command, the client responds with the output.
All communications between the client and the C&C are encrypted with AES and XOR. The crypto seems to be performed with a slightly modified implementation of AES and SHA1 from the PolarSSL library. The AES keys are generated from the first forty (40) bytes coming from the C&C. While the keys are constant during the entire communication, two different hardcoded XOR keys are used, one for incoming traffic and one for outgoing traffic.
Furthermore, the malware will not act upon any instruction unless the first packet received from the C&C matches a hardcoded key 16 bytes long, as seen in the picture below. The client will also add that key to the first response it will send to the C&C.
Finally, a custom SHA1-based hash is appended to every information packet going to and from the C&C for authentication and integrity checking purposes:
hash = SHA1(key1 + sha1(key2 + encrypted_packet_content + packet_number)) where key1 and key2 are two 64-byte strings derived from the first XOR key
During our investigation, we observed a live dialog between the C&C and our test machine. The timing and nature of the instructions received from the C&C lead us to believe that they were being manually typed by a human. Here are a few interesting pieces:
After some filesystem browsing, the C&C issued two File Upload instructions targeting one Keychain file and the Safari’s cookies store. The purpose here clearly is information stealing.
A lot of effort has been put into the network protocol, which is quite involved. The operators seemed to have a real interest in hiding the raw communication from a network dump so as to make reverse engineering more difficult. However, the use of symmetric cryptography makes it so that it is totally possible to reproduce the encryption and decryption routines and analyze the communication on-the-fly.
This attack is another reminder to stay current with OS patches as Apple patched this vulnerability in Java for Mac OS X 10.7 Update 1 and Java for Mac OS X 10.6 Update in November 2011.
ESET security software (including ESET Cybersecurity for Mac) since signature update 7001 detects this threat as OSX/Lamadai.A. Some AV vendors flagged the file as OSX/Olyx, a previous Mac malware. We did not find any relation between the two threats, the network protocol and obfuscation techniques being different.
MD5 of the files analyzed:
39084b60790ca3fdebe1cd93a4764819 file-mac.tmp (OSX payload)
MD5 of related files
7f7cbc62c56aec9cb351b6c1b1926265 file-win.tmp (Win32 payload)
dd7421fb6ca03c5752a06cffb996285a index.jar (OSX/Linux dropper)
2d86dce83851f76493ba0492d066c095 default.jar (Win32 dropper)
4b6eb782f9d508bbe0e7cfbae1346a43 index.html (HTML serving the droppers)
Thanks to Marc-Étienne M. Léveillé who performed the technical analysis.
Alexis Dorais-Joncas
Author Alexis Dorais-Joncas, We Live Security
Follow Us
Automatically receive new posts via email:
Delivered by FeedBurner
ESET Virus Radar
Archives
Select month
Copyright © 2013 ESET, All Rights Reserved.
|
{
"url": "http://www.welivesecurity.com/2012/03/28/osxlamadai-a-the-mac-payload/?wpmp_switcher=desktop",
"source_domain": "www.welivesecurity.com",
"snapshot_id": "crawl=CC-MAIN-2013-48",
"warc_metadata": {
"Content-Length": "63161",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:2WRRNBNOYXPVMGTH5QU663WSEAF7POAM",
"WARC-Concurrent-To": "<urn:uuid:1c1ace9a-eadb-46cf-a5c5-a3229a4b9d85>",
"WARC-Date": "2013-12-12T13:52:08Z",
"WARC-IP-Address": "84.233.195.46",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:L3R3574GPQOGK673FHVJVAKC3Y2VM77A",
"WARC-Record-ID": "<urn:uuid:6b72e6bd-cc12-4e68-a795-9eb494fe778c>",
"WARC-Target-URI": "http://www.welivesecurity.com/2012/03/28/osxlamadai-a-the-mac-payload/?wpmp_switcher=desktop",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:70ea5128-419b-4787-84fc-f01a25e1f4f2>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-33-133-15.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2013-48\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web with URLs provided by Blekko for Winter 2013\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
31,
32,
535,
536,
684,
685,
821,
822,
1063,
1064,
1317,
1318,
1702,
1703,
2124,
2125,
2210,
2211,
2308,
2309,
2442,
2443,
2549,
2550,
2987,
2988,
3243,
3244,
3396,
3397,
3546,
3547,
3803,
3804,
3806,
3807,
3809,
3810,
3996,
3997,
4402,
4403,
4590,
4591,
4908,
4909,
4936,
4997,
4998,
5019,
5082,
5146,
5208,
5281,
5282,
5355,
5356,
5377,
5378,
5424,
5425,
5435,
5436,
5479,
5480,
5504,
5505,
5522,
5523,
5532,
5533,
5546
],
"line_end_idx": [
31,
32,
535,
536,
684,
685,
821,
822,
1063,
1064,
1317,
1318,
1702,
1703,
2124,
2125,
2210,
2211,
2308,
2309,
2442,
2443,
2549,
2550,
2987,
2988,
3243,
3244,
3396,
3397,
3546,
3547,
3803,
3804,
3806,
3807,
3809,
3810,
3996,
3997,
4402,
4403,
4590,
4591,
4908,
4909,
4936,
4997,
4998,
5019,
5082,
5146,
5208,
5281,
5282,
5355,
5356,
5377,
5378,
5424,
5425,
5435,
5436,
5479,
5480,
5504,
5505,
5522,
5523,
5532,
5533,
5546,
5589
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 5589,
"ccnet_original_nlines": 72,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3193950057029724,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.07206405699253082,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.20106762647628784,
"rps_doc_frac_unique_words": 0.5,
"rps_doc_mean_word_length": 5.261124134063721,
"rps_doc_num_sentences": 64,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 5.4399518966674805,
"rps_doc_word_count": 854,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.02448252961039543,
"rps_doc_frac_chars_dupe_6grams": 0.008012459613382816,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.012241260148584843,
"rps_doc_frac_chars_top_3gram": 0.008012459613382816,
"rps_doc_frac_chars_top_4gram": 0.004451369866728783,
"rps_doc_books_importance": -488.0901184082031,
"rps_doc_books_importance_length_correction": -488.0901184082031,
"rps_doc_openwebtext_importance": -318.54443359375,
"rps_doc_openwebtext_importance_length_correction": -318.54443359375,
"rps_doc_wikipedia_importance": -188.63609313964844,
"rps_doc_wikipedia_importance_length_correction": -188.63609313964844
},
"fasttext": {
"dclm": 0.04334735870361328,
"english": 0.9117759466171265,
"fineweb_edu_approx": 1.997482180595398,
"eai_general_math": 0.4090145230293274,
"eai_open_web_math": 0.2433156967163086,
"eai_web_code": 0.269794762134552
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.822",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.02",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "4",
"label": "Analyze"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "10",
"label": "Knowledge Article"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "4",
"label": "Advanced Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "4",
"label": "Graduate/Expert Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
1,369,549,260,280,180,200
|
W3C home > Mailing lists > Public > public-html@w3.org > April 2010
Re: General Response to the Accessibility Task force on Issues 90, 91, 93, 96, 97
From: Laura Carlson <laura.lee.carlson@gmail.com>
Date: Thu, 22 Apr 2010 16:04:53 -0500
Message-ID: <y2t1c8dbcaa1004221404q5f89483bi78054256865bf60f@mail.gmail.com>
To: HTMLWG WG <public-html@w3.org>
fyi...
---------- Forwarded message ----------
From: Laura Carlson <laura.lee.carlson@gmail.com>
Date: Thu, 22 Apr 2010 15:37:01 -0500
Subject: Re: General Response to the Accessibility Task force on
Issues 90, 91, 93, 96, 97
To: Janina Sajka <janina@rednote.net>, "Michael(tm) Smith"
<mike@w3.org>, Shelley Powers <shelley.just@gmail.com>
Cc: HTML Accessibility Task Force <public-html-a11y@w3.org>, John
Foliot <jfoliot@stanford.edu>
> we have numerous items on our collective plate.
This is true. Jon G, mentioned this on the survey that "I think the
more we can simplify HTML 5 elements the easier it will be to get HTML
5 and accessibility implemented and to explain to authors how to
create accessible content in HTML5. Browser developers will probably
not implement these elements anyway if they don't like them or do it
inconsistently. There is a lot in HTML5 and I think we have enough to
discuss without spending time on elements that may never be
implemented."
Jim Allan commented further on implementation, "Creation of orphaned,
poorly implemented or non-implemented elements is not the goal. Having
rich semantics that do not require an accessibility api to function
(not all people with disabilities use AT) is laudable. But, only if
implemented. Current implementations - 0, aria workarounds - 5."
Sean commented about making the case,"I think this needs more work in
the justification before its advanced to the WG. I'm not convinced by
the arguments we are currently putting forward, nor the manner in
which we are expressing them. However I'm not fundamentally opposed to
the idea that semantic elements are good for accessibility, but we
havent really made that case. Clearly we aren't in a position to
include every semantic element that might be required, so some
assembly will still be required by authors, if we include aria to make
those accessible, its not clear to me what is special about these
elements."
I share these same concerns.
The biggest concern at this point is the one Sean's had in the manner
in which the task force expressed the resolution and lack of
rationale. Shelley, I apologize for this.
I tried to go through the a11y TF face to face minutes and list out all of the
the rationale that I could find for each of your issues. Corrections
and additions from the task force members would be appreciated.
<figure>
* It's a landmark that is useful. there was a lot of argument about
the content model. Shelley said it should be just images, but people
suggested that almost anything could be a figure. People want the
language to be descriptive not prescriptive.
* Figure associates stuff. In general, semantic elements that have no
behaviour aren't used well (HTML is full of examples) but more
semantic elements that do have behaviour are useful.
* Not sure there is browser behaviour associated - maybe on certain
types of devices but UA isn't expected to do anything with it.
* If we want the figure to be equivalent to aria-labelledby we would
need figcaption to be available outside <figure>. Complete equivalence
between figure and aria-labelledby would require the figcaption can go
anywhere and have a pointer to the caption.
* Browsers on small screens can use these to linearise helpfully, and
think that is valuable
* Native semantics for these are better than annotation+style+ARIA.
<aside>
* Native semantics for these are better than annotation+style+ARIA.
* Browsers on small screens can use these to linearise helpfully, and
think that is valuable
* Magnifiers have a valid use case for changing layout based on the semantics.
* aside is WAY to vague a catch-all.
* expect the landmark elements will eventually have browser behavior,
particularly on small-screen devices.
<details>
* Specific behaviour associated.
* Makes a control for a behavior that is frequently done in script.
what details does is frequently done (badly and inaccessibly) in
script.
* Specifically useful for accessibility.
* Authors often roll their own without getting the accessibility
right, and it is expensive.
* Details isn't trivial to do in Javascript.
* There are things without elements, like accordions - I'd like to see
elements for those too, rather than removing this one...from an
interaction design perspective she might have a point that these are
similar.
<progress>
* Has specific behaviour associated.
* People want the native semantics.
* For the progress element, there are things that don't work as well
as the aria approach
* Should be improved, not removed.
* Not convinced any of these new elements will be used widely. They
may end up unloved like kbd, but they are useful and I wouldn't remove
them.
* Shouldn't it be noted that the hidden attribute is read-only?
* For the progress element, there are things that don't work as well
as the aria approach
<meter>
* Has specific behaviour associated.
<hidden>
* Not so strong on keeping the hidden attribute.
* Hidden does what the ARIA equivalent does, and seems useful.
* Could live without it given we will get it in aria.
* It's like display:none but without the nasty side effects.
* It is slightly different from aria-hidden...
* HTML5 hidden applies to ALL elements
* Not sure this has an accessibility impact...
* There is some impact (but not a lot).
Best Regards,
Laura
--
Laura L. Carlson
Received on Thursday, 22 April 2010 21:05:26 UTC
This archive was generated by hypermail 2.3.1 : Monday, 29 September 2014 09:39:17 UTC
|
{
"url": "http://lists.w3.org/Archives/Public/public-html/2010Apr/1144.html",
"source_domain": "lists.w3.org",
"snapshot_id": "crawl=CC-MAIN-2014-52",
"warc_metadata": {
"Content-Length": "16642",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:CQ7VNYDBUVDOQC25HBDKI7SL4UPXEGNM",
"WARC-Concurrent-To": "<urn:uuid:fbc58751-6e56-4281-a438-45fef12a27b3>",
"WARC-Date": "2014-12-29T12:31:42Z",
"WARC-IP-Address": "128.30.52.56",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:ITVXQJAK3EPM3TKELPEIVTQFOSYFOLWM",
"WARC-Record-ID": "<urn:uuid:df1148b7-1aa4-4125-9aed-f88e7986125d>",
"WARC-Target-URI": "http://lists.w3.org/Archives/Public/public-html/2010Apr/1144.html",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:632edace-b6fa-4f08-b574-281be76ed3f7>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-231-17-201.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2014-52\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web with URLs provided by Blekko for December 2014\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
68,
69,
151,
152,
202,
240,
317,
352,
359,
360,
400,
450,
488,
553,
579,
638,
693,
759,
789,
790,
840,
841,
909,
980,
1045,
1114,
1183,
1253,
1313,
1327,
1328,
1398,
1469,
1537,
1605,
1670,
1671,
1741,
1811,
1877,
1948,
2015,
2080,
2143,
2214,
2280,
2291,
2292,
2321,
2322,
2392,
2453,
2495,
2496,
2575,
2644,
2708,
2709,
2718,
2786,
2855,
2921,
2966,
3036,
3099,
3152,
3220,
3283,
3352,
3423,
3494,
3538,
3608,
3631,
3699,
3700,
3708,
3776,
3846,
3869,
3948,
3985,
4055,
4093,
4094,
4104,
4137,
4205,
4270,
4278,
4319,
4384,
4412,
4457,
4528,
4592,
4661,
4670,
4671,
4682,
4719,
4755,
4824,
4845,
4880,
4948,
5019,
5025,
5089,
5158,
5179,
5180,
5188,
5225,
5226,
5235,
5284,
5347,
5401,
5462,
5509,
5548,
5595,
5635,
5636,
5650,
5656,
5660,
5677,
5726,
5727
],
"line_end_idx": [
68,
69,
151,
152,
202,
240,
317,
352,
359,
360,
400,
450,
488,
553,
579,
638,
693,
759,
789,
790,
840,
841,
909,
980,
1045,
1114,
1183,
1253,
1313,
1327,
1328,
1398,
1469,
1537,
1605,
1670,
1671,
1741,
1811,
1877,
1948,
2015,
2080,
2143,
2214,
2280,
2291,
2292,
2321,
2322,
2392,
2453,
2495,
2496,
2575,
2644,
2708,
2709,
2718,
2786,
2855,
2921,
2966,
3036,
3099,
3152,
3220,
3283,
3352,
3423,
3494,
3538,
3608,
3631,
3699,
3700,
3708,
3776,
3846,
3869,
3948,
3985,
4055,
4093,
4094,
4104,
4137,
4205,
4270,
4278,
4319,
4384,
4412,
4457,
4528,
4592,
4661,
4670,
4671,
4682,
4719,
4755,
4824,
4845,
4880,
4948,
5019,
5025,
5089,
5158,
5179,
5180,
5188,
5225,
5226,
5235,
5284,
5347,
5401,
5462,
5509,
5548,
5595,
5635,
5636,
5650,
5656,
5660,
5677,
5726,
5727,
5813
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 5813,
"ccnet_original_nlines": 131,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.37560975551605225,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.028455279767513275,
"rps_doc_frac_lines_end_with_ellipsis": 0.022727269679307938,
"rps_doc_frac_no_alph_words": 0.24796748161315918,
"rps_doc_frac_unique_words": 0.43400445580482483,
"rps_doc_mean_word_length": 5.093959808349609,
"rps_doc_num_sentences": 75,
"rps_doc_symbol_to_word_ratio": 0.0032520298846066,
"rps_doc_unigram_entropy": 5.457581520080566,
"rps_doc_word_count": 894,
"rps_doc_frac_chars_dupe_10grams": 0.09090909361839294,
"rps_doc_frac_chars_dupe_5grams": 0.139218270778656,
"rps_doc_frac_chars_dupe_6grams": 0.139218270778656,
"rps_doc_frac_chars_dupe_7grams": 0.139218270778656,
"rps_doc_frac_chars_dupe_8grams": 0.139218270778656,
"rps_doc_frac_chars_dupe_9grams": 0.11506368219852448,
"rps_doc_frac_chars_top_2gram": 0.0054896799847483635,
"rps_doc_frac_chars_top_3gram": 0.01449275016784668,
"rps_doc_frac_chars_top_4gram": 0.008344310335814953,
"rps_doc_books_importance": -507.990478515625,
"rps_doc_books_importance_length_correction": -507.990478515625,
"rps_doc_openwebtext_importance": -299.14483642578125,
"rps_doc_openwebtext_importance_length_correction": -299.14483642578125,
"rps_doc_wikipedia_importance": -198.4007568359375,
"rps_doc_wikipedia_importance_length_correction": -198.4007568359375
},
"fasttext": {
"dclm": 0.38982093334198,
"english": 0.9291453957557678,
"fineweb_edu_approx": 1.8746799230575562,
"eai_general_math": 0.5989976525306702,
"eai_open_web_math": 0.3795992136001587,
"eai_web_code": 0.5339179039001465
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.678",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "005.467",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "4",
"label": "Analyze"
},
"secondary": {
"code": "5",
"label": "Evaluate"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "18",
"label": "Q&A Forum"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "4",
"label": "Advanced Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "4",
"label": "Graduate/Expert Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-7,607,864,893,272,521,000
|
all 84 comments
[–]ehird 8 points9 points * (16 children)
sorry, this has been archived and can no longer be voted on
My thoughts:
I believe this approach, including the removal of the BufferedSource type, makes things a lot more simple and elegant.
I don't think the single-type approach will be too confusing to beginners: you can explain Conduit a m b as "transforms a stream of as into a stream of bs", and Pipe i o m r is basically the same: "transforms a stream of as into a stream of bs, producing a final result r". Indeed, when I first read up on conduit, before pipes existed, I thought that Source, Sink and Conduit sounded very similar, and I saw a lot of duplication in their constructors; perhaps my experience of not typical of a beginner, but I think the unnecessary differentiation and duplication of these concepts confused me rather than helped.
I don't think newtype wrappers are a good idea; you'll lose the conceptual simplicity that comes from . Sure, it means you won't be able to hide the existence of Pipe from users, but you shouldn't do that, anyway. It's not like iteratees, where types like Enumeratee hid complicated underlying types; Source, Sink and Conduit simply become shorthand for established concepts.
As far as the Monad instance, I don't think it's that big a deal. Perhaps Conduit should be changed so that Conduit i o m is Pipe i o m (), to emphasise the relation between the two, and to not make people expect the Monad instance to behave as it previously did. I always found having the monad be the middle parameter strange, anyway, even though I understood the reason (to allow a MonadTrans instance); since that reason is gone, moving it to the front or the back seems like a good idea to me. Were it not for the order chosen by Pipe (for the same reason), I'd suggest the front, but Conduit ByteString Blah IO seems fine to me. It's a conduit from ByteStrings to Blahs in IO.
As I said in the previous thread, I think Void is a better choice for Source's input than (). (Edit: Although, it seems like the early termination branch when input demanded is more or less another Source (to allow providing output after all input is exhausted), so this might not apply.)
I think that keeping around (=$) and ($=) will confuse more than it helps; it provides additional specialisation of the types, but at the cost of making people think there's three different notions of composition at work, when in fact there is only one. Again, don't try to hide Pipe behind Source, Sink, and Conduit; let Pipe be the main concept, and the three type synonyms merely handy aliases for common uses. I realise this goes against the name of the package somewhat, but, well, "pipe" would just be confusing :)
BTW, I understood your point in the original thread, and I'm not attempting to rekindle the flames — this blog post demonstrates that things go much better when people are cooperating, after all — but you seemed overly defensive, which (to me) seemed a strange reaction to an attempt to improve conduit. It's true that some of the claims might have been premature, but at least to me, and I expect to twanvl and the others defending the proposal in that thread, the duplication in conduit's types seemed obvious enough that it wasn't an unfounded assertion to say they could be simplified through unification, even without a proof that the composition operators could be unified. Certainly, I'd rather we have proposals for improving libraries that might make claims a little prematurely than to have people hold back on suggestions because they haven't yet rewritten an entire codebase to use them.
Again, not trying to accuse anybody of anything; just offering my perspective on the disagreement.
Edit: Also, I'm not sure why you say you can't do lazy IO with pipes. Does this translation of lazyConsume not work?
lazyConsume :: (MonadBaseControl IO m, MonadActive m) => Source m a -> m [a]
lazyConsume (Done mv ()) = maybe (return []) absurd mv
lazyConsume (HaveOutput src _ x) = (x:) <$> lazyConsume src
lazyConsume (NeedInput isrc _) = lazyConsume $ isrc ()
lazyConsume (PipeM msrc _) = liftBaseOp_ unsafeInterleaveIO $ do
a <- monadActive
if a
then msrc >>= lazyConsume
else return []
Edit: Oh, you were referring to the pipes package itself, rather than pipes in general. (This is going to get confusing...)
[–]snoyberg[S] 2 points3 points (5 children)
sorry, this has been archived and can no longer be voted on
Don't worry about rekindling flames here. Perhaps I came off too harsh, it was not my intent. I was just trying to be direct. I'll tone it down in the future to avoid hurt feelings.
Thanks for the feedback here. I'm hesitant to change the order of parameters in Conduit, simply because if we avoid doing so old code works. It's pretty cool that a large subset of code that worked with conduit 0.0 still works with 0.4.
As for the operators: currently $$ and $$& are not simply aliases for pipe. The former also applies runPipe, while the latter is both runPipe and pipeResume. The other three operators are just synonyms. I'll at least keep the old versions in for the next version, though I'll consider deprecating them. I'm not quite sure how I feel about it over all.
[–]Tekmo 2 points3 points (0 children)
sorry, this has been archived and can no longer be voted on
Don't be afraid of breaking changes. I think it's implied that if a package is v0.* to expect major changes.
[–]ehird 1 point2 points (3 children)
sorry, this has been archived and can no longer be voted on
Thanks for the feedback here. I'm hesitant to change the order of parameters in Conduit, simply because if we avoid doing so old code works. It's pretty cool that a large subset of code that worked with conduit 0.0 still works with 0.4.
Yeah, it's not a big deal, although if you're going to break backwards compatibility, now would be an excellent time :)
And yes, I was only referring to the three composition operators; the others are definitely different. (I think ($$+) would be a nicer name than ($$&); the & is too visually similar to the $.)
[–]dnulu 6 points7 points (0 children)
sorry, this has been archived and can no longer be voted on
How about ($$-) instead. Then
(src2, headers) <- src $$- getHeaders
could be read as "src2 is src minus the headers"
[–]vagif 2 points3 points (1 child)
sorry, this has been archived and can no longer be voted on
I would like to support suggestion of breaking compatibility. Conduits are still in flux. If new interface gives any advantages i think it's worth breaking from the old code. In the end you guys were not shy to break Yesod API many times :) But i agree that it pays off.
[–]snoyberg[S] 2 points3 points (0 children)
sorry, this has been archived and can no longer be voted on
I agree that it's worth breaking the API for a good reason. I'm just not convinced that this is a solid reason to change, in which case inertia comes into play. More to the point: almost every type out there keeps the monadic as the penultimate parameter for the purpose of the MonadTrans instance, so the current form feel natural to me anyway.
[–]apfelmus 0 points1 point (9 children)
sorry, this has been archived and can no longer be voted on
Concerning Void for input, the comments on Twan's post discuss that, it's not the right thing to do.
If you ignore resource usage, the semantics of Pipe are
type Pipe i o m a = [i] -> m ([o],a)
You can't output Void, so setting o = Void is ok. But when you get a Void as an input, you can make anything from it, literally:
anything :: forall a. Void -> a
-- the empy line right above contains all the pattern matches
-- we need to consider to define the function anything
So, if you ever get Void as an input, you can make yourself a millionaire, among other things.
[–]snoyberg[S] 2 points3 points (7 children)
sorry, this has been archived and can no longer be voted on
I don't know which is the better approach, but I'm not convinced by this argument. Why is it acceptable in conduit itself to call absurd, but for someone writing a Source it's not?
[–]ehird 2 points3 points (5 children)
sorry, this has been archived and can no longer be voted on
The point is that a Pipe would be able to demand a Void from the conduit code, which would (obviously) be unable to supply one. What you really want is a type Contravoid such that there are no values of Contravoid -> r for any r, but there's no such type in Haskell.
(I realise this change of opinion contradicts my original post; see here.)
[–]snoyberg[S] 1 point2 points (4 children)
sorry, this has been archived and can no longer be voted on
I believed that at first as well, but this pull request demonstrates that we can just use the second record of the NeedInput constructor.
[–]polveroj 1 point2 points (1 child)
sorry, this has been archived and can no longer be voted on
Is there a reason not to raise some sort of error in addition to closing the pipe when an invalid constructor is encountered? This is the sort of programmer error that I think deserves a loud failure rather than a silent one.
[–]ehird 1 point2 points (0 children)
sorry, this has been archived and can no longer be voted on
Whether the input type is () or Void, it's not an error; in the latter case, you asked for an input, and the library replied that there is none; in the former case, you asked for an input, and the library helpfully supplies the only possible one.
There's no reason you shouldn't be able to use pipes that can take useful input (but don't require it) as sources.
[–]ehird 1 point2 points (0 children)
sorry, this has been archived and can no longer be voted on
Well, yes; that's the original comment that convinced me it was a good idea.
But, if you look at the second field of the NeedInput constructor, it's just another source! (modulo the r parameter)
That is, the second field of NeedInput is "a source to use if there's no more input". Having an inconsistency from a source-before-it-requests-its-first-input and a source-after-that is weird, so I think () is actually the correct choice.
[–]ehird 0 points1 point * (0 children)
sorry, this has been archived and can no longer be voted on
Wait a second, I think I've changed opinion back again. Replace the second field of NeedInput with Input i o m r, keeping the input type. Then, you can use Void as the input to a source, and "source before asking for input" and "source after asking for input" are the same.
Edit: Oh, I see now how the pull request works — you can of course use Void as the input type for the "no more input" field, and the end result is that you know that field will always be picked, since you can't call a function taking Void. OK, I'm happy.
[–]apfelmus 0 points1 point (0 children)
sorry, this has been archived and can no longer be voted on
Now that you say it, I'm hesitant again. However, note that someone a source will never call absurd, that's only needed if you obtain a value of Void, which you can then convert into anything you like.
One of the argument in the comments section was actually different.
[–]ehird 1 point2 points (0 children)
sorry, this has been archived and can no longer be voted on
Well, the point was that you can demand a Void, but the conduit code will simply the other option it has: early termination.
However, as I said in my edit, as the early termination for a demand of input is another Pipe with an input of (), this doesn't work.
[–]simonmar 8 points9 points (9 children)
sorry, this has been archived and can no longer be voted on
As a general comment, I'm finding this much more accessible than the previous Conduit implementation. Perhaps that's just because each time I run at the hill I get a little further up, but I was definitely confused by the three different types with apparent similarities before.
Could you explain the role of the "leftover" field of Done? I don't see it being instantiated with a Just anywhere in the core functionality (Data.Conduit.Internal), but it is filled in with Just in a couple of places in Data.Conduit.List.
How do exceptions work?
In Data.Conduit, the docs for the Pipe type mention the "pipe" function, but it isn't exported by Data.Conduit.
[–]snoyberg[S] 1 point2 points (8 children)
sorry, this has been archived and can no longer be voted on
All good questions.
Leftover is for Sinks which return some unconsumed data. A simple example would be Data.Conduit.Binary.head: it wants to take one byte off of the next ByteString in the stream, and then return the rest of the ByteString for the following Sink to consume.
As it stands now, you can't catch exceptions in a Pipe. That could be implemented, but I don't think it's necessary. The idea of BufferedSource (or now, connect-and-resume) is that you can have your Pipe do a small amount of a computation, and then return to your main monad for the rest of it.
As for resource allocation, ResourceT ensures that any resources acquired will be automatically cleaned up when an exception is thrown. That's why functions like sourceFile need to live in a MonadResource instead of just a Monad.
pipe is in Data.Conduit.Internal. I'll update the docs to turn it into a link.
[–]simonmar 1 point2 points (7 children)
sorry, this has been archived and can no longer be voted on
Regarding leftovers: there seems to be some conceptual similarity between the leftover field of Done and pipeResume. Something feels a bit strange about the design here, but I can't immediately envisage a way to simplify it.
[–]snoyberg[S] 1 point2 points (6 children)
sorry, this has been archived and can no longer be voted on
They're definitely related to each other. One of the main purposes for pipeResume is to retain the leftover values in its return left Pipe. You can also see the leftover values being used in monadic bind.
Leftovers is a concept that I think every library (iteratee, enumerator) implements except pipes. I'm still not quite certain how pipes would deal with those use cases. (For that matter, I also don't understand how await returns a instead of Maybe a.)
[–]simonmar 1 point2 points (5 children)
sorry, this has been archived and can no longer be voted on
I think it's pretty clear you want the Maybe version of await. Paulo had it in his "guarded pipes", called tryAwait: http://pcapriotti.wordpress.com/2012/02/02/an-introduction-to-guarded-pipes/
What seems strange about the leftovers is that you can only have zero or one input element leftover. Having "unawait" would subsume leftovers, and seems more natural (if it could be made to work).
[–]snoyberg[S] 1 point2 points (3 children)
sorry, this has been archived and can no longer be voted on
It was actually an explicit design decision to form leftovers to only every be 0 or 1 elements. This all comes down to data loss rules: even though theoretically we could use lists of values for NeedInput or HaveOutput, the entire library restricts itself to dealing with single elements at a time, to make sure we never consume too much input at one stage which is then lost.
I'm not really sure how unawait would be implemented without having something like the current setup of the Done constructor, can you clarify?
[–]pcapriotti 1 point2 points (2 children)
sorry, this has been archived and can no longer be voted on
I had written a ChunkPipe type for that purpose, but that turned out not to satisfy the Monad laws.
I think the best approach so far to implement something like "unawait" is in this pull request: https://github.com/pcapriotti/pipes-extra/pull/3.
By the way, I don't think this is a shortcoming of Pipes. There seems to be some fundamental problem with unawait that breaks the category laws. As I think associativity of composition is the most important property that a stream processor library should satisfy, unawait is necessarily going to be a second class citizen.
I wrote in some other comment that I don't think it's such a big problem in practice, since you can split your input in "independent chunks" early in the pipeline, then forget about possible leftovers alltogether.
[–]snoyberg[S] 1 point2 points (1 child)
sorry, this has been archived and can no longer be voted on
Well, obviously I can't convince you that it is a big deal. All I can say is that those of us who tried to work under the model you're describing with enumerator found it a sufficiently big enough deal to warrant creating conduit in the first place. This is why I'm so adamant that a good library for this stuff can't be written without strong motivating use cases: you won't have any real understanding of what is important and what isn't.
Can you show me some code for your "split your input" approach? I have no idea how it would work.
[–]pcapriotti 2 points3 points (0 children)
sorry, this has been archived and can no longer be voted on
Actually I agree that it's important, and in fact I claim that it is implementable in pipes, so it can't be the reason why one would choose one over the other. It's just not part of the primitives, although I suppose it could be integrated more strictly for performance reasons.
The "split your input" approach I was referring to is creating a pipe of the form:
Pipe ByteString ByteString m r
which takes input chunks and splits them along their "natural" boundaries. For example, in an http server, you would look for the separator between header and body (double crlf I believe?) and split there, emitting the two pieces as separate chunks, so that successive stages in the pipeline don't need to bother with leftover values. If a chunk doesn't contain a separator, you'd just yield it as is, so that the pipe works as the identity (hence it doesn't have any effect, because of the category laws) away from boundaries.
If this approach is not feasible for some reason, you can still use something like PutbackPipe to carry leftovers. It just requires some boilerplate to be used inside a pipeline.
This is why I'm so adamant that a good library for this stuff can't be written without strong motivating use cases: you won't have any real understanding of what is important and what isn't.
Yes, that's definitely true, and that's why I consider feedback from "conduit people" very valuable. However, I think the approach of starting from the "abstract" and gradually compromising towards practicality is also valid.
I'm happy to see that the two approaches are converging towards some middle ground.
[–]snoyberg[S] 0 points1 point (0 children)
sorry, this has been archived and can no longer be voted on
I thought about it a bit, and I came up with an approach using a separate Leftover constructor. I pushed a commit to a separate branch.
I'm not convinced that this is a good idea, since it erodes further some of our invariants. In particular, I'm not sure if we want to allow a Pipe to return leftovers at any arbitrary point in the computation. That said, there is a certain attraction of, once again, decoupling two actions into separate constructors.
[–]twanvl 3 points4 points (17 children)
sorry, this has been archived and can no longer be voted on
One exciting thing that is possible with the pipes interface is writing conduits and sources in monadic style using the combinators
yield :: o -> Pipe i o m () -- = o -> Conduit i m o
await :: Pipe i o m i
Or with the handling of closing pipes:
closeOrYield :: m () -> o -> Pipe i o m ()
tryAwait :: Pipe i o m (Maybe i)
Some other functions can also get a simpler type. haveMore no longer needs a 'next' conduit, you can just use haveMore' close xs >> next.
haveMore' close = foldM (closeOrYield close)
Something similar might be possible for sequenceSink (I don't really like the name sequence, because it conflicts with Control.Monad.sequence).
sequence sink = forever $ do
x <- noOutput sink
yield x
As I write this, I realize that you need a noOutput function to match noInput, that converts a Pipe i Void m r into a Pipe i o m r. A nicer way to handle this is using a universal quantifier,
type Sink m i r = forall o. Pipe m i o r
type Source m i r = forall i. Pipe m i o r
type Composition m r = forall i o. Pipe m i o r
I am not saying you should actually do this, but it is something to consider for the pipe-theorists.
[–]polveroj 5 points6 points (0 children)
sorry, this has been archived and can no longer be voted on
As someone who prefers not to write CPS-transformed code by hand, I'm a big fan of await and yield over using the Pipe constructors directly.
Using polymorphism to express that a Pipe doesn't care about its input or output is cute, but I don't think it's worth the complexity in the types and the type errors. Using polymorphic conversion functions seems like a fine tradeoff.
It might also improve error messages to make NoInput and NoOutput two type synonyms for Void.
[–]pcapriotti 1 point2 points (0 children)
sorry, this has been archived and can no longer be voted on
I considered this, and decided it's not a good idea, because it removes opportunities for the type-checker to find mistakes. If you really want a Producer (i.e. Source) to behave polymorphically, you can use: pipe (const ()) >+> producer. With a Consumer (i.e. Sink), you would write consumer >+> pipe absurd.
[–]snoyberg[S] 1 point2 points (13 children)
sorry, this has been archived and can no longer be voted on
Didn't I read that there were some issues with a yield function? I know under conduit 0.3 I specifically list it as a function that can't be implemented, but that's because it would be implemented as a Sink providing leftovers that were never fed to it. Overall, I still prefer the approach of writing the functions directly, but that could just be because I'm more comfortable with it still.
And the foralls definitely make me nervous, I'm far from ready to embrace that. I still want to bring the rest of the conduit code up-to-date with the current changes to make sure it actually works.
[–]ehird 1 point2 points (12 children)
sorry, this has been archived and can no longer be voted on
For what it's worth, when initially trying to understand the various approaches to stream processing, the need to write my own constructors and do "manual plumbing", as it were, felt very strange and low-level to me. Being able to write individual stream processors (that don't come under some common higher-order pattern) as simple loops of reading and writing values would be much better, IMO, especially since you can use standard patterns like lift to run an action in the base monad; since Pipe falls neatly into standard interfaces like Monad and MonadTrans, there's no reason to make people reimplement the instances to use the functionality.
By the way, the documentation of Pipe in Data.Conduit references the pipe function, but it isn't exposed from that module. (Speaking of which, I feel like pipe's first parameter should be polymorphic in its result type; I realise the result is discarded, but it seems strange to require there to be no result just because of this; it's like (>>) having the type (Monad m) => m () -> m a -> m a.)
[–]snoyberg[S] 1 point2 points (11 children)
sorry, this has been archived and can no longer be voted on
I don't have a problem with adding the await and yield functions, assuming they don't present any issues (was I wrong that yield violated some invariants? I was sure I read that somewhere). But I don't think I'll be basing everything in the package off of those quite yet. Maybe after some performance analysis it will make sense.
[–]cdsmith 1 point2 points (10 children)
sorry, this has been archived and can no longer be voted on
I'm sure there have been lots of discussions on this in many places... but it's possible you're remembering the discussion on haskell-cafe about an 'unawait' for pipes, which is different from yield. It's true that unawait does indeed break composition in the sense of violating category laws. I'm not sure if your new conduit plans to satisfy the category laws or not... ideally it would, but combining that with useful error handling and early resource cleanup is a tricky problem.
[–]snoyberg[S] 2 points3 points (0 children)
sorry, this has been archived and can no longer be voted on
Yes, it was unawait. I remember noticing that because it had the same problem as enumerator's yield. Thanks!
[–]donri 1 point2 points (8 children)
sorry, this has been archived and can no longer be voted on
Or perhaps he's thinking of pipes-core vs pipes proper?
[–]cdsmith 1 point2 points (7 children)
sorry, this has been archived and can no longer be voted on
The semantics of pipes in both packages are the same in the ways that matter here... neither one can implement unawait while still offering a working Category instance. Or at the very least, not one that makes pipe a functor from Hask to PipeC m r. It's possible you could get Category working -- I haven't checked -- but only at the expense of making idP into some grafted-on kludge.
[–]Tekmo 1 point2 points (4 children)
sorry, this has been archived and can no longer be voted on
No, you were correct the first time. You can't communicate upstream or artificially restore control upstream without violating the category laws. This always breaks the identity law, no matter how monstrous of a kludge you make idP.
[–]cdsmith 1 point2 points (3 children)
sorry, this has been archived and can no longer be voted on
The proposal that finished out that thread was to add unawait with the semantics given (loosely... I skipped plumbing of return values so these don't type-check, but it's doable) by rewrite rules like this:
unawait x >> lift m ==> lift m >> unawait x
unawait x >> yield y ==> yield y >> unawait x
unawait x >> await ==> return x
So no information is really moving upstream at all. Then you define composition to just throw away the downstream unawaits (eww... I know, but it still follows the category laws), and that does end up being associative, just without an identity. So then you graft on an artificial idP:
data Pipe a b m r where
IdP :: Pipe a a m r
RealPipe :: ... -> Pipe a b m r
Which is a silently discarded in >+>, and silently converted to pipe id when composed monadically. The result is a Monad and a Category, but really doesn't act like you'd hope. I left off thinking to myself that I should ask what other laws we should be expecting, that would forbid just throwing away information like that. But I never thought it through in detail.
[–]cdsmith 1 point2 points (1 child)
sorry, this has been archived and can no longer be voted on
Oh, but (and this didn't come up then, I just realized it now) this couldn't be made into a correct MonadTrans instance, because you have the law lift . return == return, and there's no way to recognize what is just a return in the inner monad. So you wouldn't be able to special-case >>= for return the way you would need to in order to keep the monad laws holding. So the MonadTrans instance prevents that trick.
Which is fine... it was a crime against humanity to begin with. :)
[–]Tekmo 1 point2 points (0 children)
sorry, this has been archived and can no longer be voted on
Oh, another thing I forgot to mention. The formal identity does not work (and I did try it a long time ago out of curiosity). The reason is simple: you cannot define composition in terms of it because it constrains the type of composition. If you had statements like:
IdP >+> p = p
p >+> IdP = p
... then the type-checker infers that the type of (>+>) must be:
(>+>) :: Pipe a a m r -> Pipe a a m r -> Pipe a a m r
... because that's the type of IdP.
[–]donri 1 point2 points (1 child)
sorry, this has been archived and can no longer be voted on
I was referring to this.
[–]cdsmith 1 point2 points (0 children)
sorry, this has been archived and can no longer be voted on
Sure, but in neither case does yield break the category laws. In Paolo's release, it was ensure that did so. And in the haskell-cafe thread, it was unawait.
[–]snoyberg[S] 1 point2 points (0 children)
sorry, this has been archived and can no longer be voted on
Firstly, I think it might be possible to get rid of sequenceSink entirely if I change Sink to use forall instead of Void. I'll follow up on that.
But I'm confused about await. It seems the same as Data.Conduit.List.head. The difference is that await returns i, while head returns Maybe i. So what happens with await when there's no more data in the stream?
[–]Tekmo 8 points9 points (3 children)
sorry, this has been archived and can no longer be voted on
Here, let me comment, because I've been doing TONS of work on error-handling for pipes and I want to make several observations that can help you even before I release my implementation of error handling. I've finally proven the category laws for the two combined termination-handling approaches (and I have one category left for the exception-handling before I release), so I can speak much more confidently about at least the termination-handling aspect.
My first observation is that your work to pass state between sources is basically an attempt to recapitulate the pipe monad. The pipe monad is how you pass information between multiple sources and it is why pipes distinguishes between the return value of a source and it's yielded output.
Second, the ideal iteratee library lets one communicate to upstream that it no longer requires input so that upstream can finalize itself immediately. I call this "downgrading" the current pipe to a producer (or source in your case), and you have something very similar to this in conduits. So let's imagine that there are two blocks of code:
Block A: Code that executes BEFORE the downgrade (i.e. it can await from upstream)
Block B: Code that executes AFTER the downgrade (i.e. it can't await from upstream).
The way pipes does this is simply having the first block return the second block, i.e.:
Pipe a b m (Producer b m r) -- It's actually (Fix (Producer b m)), but ignore that for now
In other words, the "Pipe" is block A and the "Producer" is block B. If you compose this with another pipe and block "A" terminates, then composition calls the upstream finalizer, installs block "B" in block "A"s place, and marks the composed pipe as no longer needing input (by returning it as a Producer).
Third, the big mistake that every other iteratee approach makes when trying to finalize upstream is to either communicate upstream or force control to upstream so that it can call finalization code. This is the #1 source of bugs and flaws in compositionality and removes any possibility of implementing a category.
In pipes, rather than artificially forcing control upstream in order to finalize upstream pipes correctly, you simply have every pipe yield the most up-to-date finalizer for itself alongside its normal yielded value. The category instance then automatically composes its own finalizer with all the finalizers upstream of it so that every pipe at any point in time has the correct finalizer to run to shut off all of upstream completely at any moment without every having to restore control upstream. Of course, the user never actually runs the finalizer (nor can they even access it). The category instance calls it automatically when the user downgrades their pipe (and thus proves that they can't await any longer).
[–]snoyberg[S] 0 points1 point (2 children)
sorry, this has been archived and can no longer be voted on
Apologies, but I'm not following all of your terminology. When you say "pass state between sources," are you talking about my BufferedSource solution? I'm wouldn't classify is as passing state between sources, it's simply not closing a Source after the Sink terminates.
In other words, the pattern of conduit is that as long as the right-hand pipe is not terminated, it tries to get data from the left-hand pipe. If the left-hand pipe terminates first, then early termination is applied to the right-hand pipe. In normal connecting ($$ and the pipe function), if the right-hand pipe terminates first, then early termination is applied to the left-hand pipe, and any leftovers from the left-hand pipe are discarded.
The connect-and-resume approach modifies that last sentence. If the right-hand pipe terminates first, then the current state of the left-hand pipe is returned, together with any leftovers from the right-hand pipe. This means we can reuse a Source from exactly where it left off.
I haven't spent much time playing with this yet (I was pretty exhausted when I got home last night), but my initial reaction is that this more elegant approach is going to turn out to be less powerful in practice. Warp, for example, needs to read some headers and then pass the Source to an Application which it can't control, and which can't be trusted to return an updated Source. So I'll basically have to reinvent part of the BufferedSource idiom anyway. It might be possible to create a modified isolate function which wraps around an IORef containing a Source and apply connect-and-resume to it, but I only woke up 10 minutes ago, so don't trust anything I say ;).
[–]Tekmo 0 points1 point (1 child)
sorry, this has been archived and can no longer be voted on
Yes, and the way you would do that using the pipe monad is:
source >+> (sink1 >> sink2)
[–]snoyberg[S] 1 point2 points (0 children)
sorry, this has been archived and can no longer be voted on
I don't think that's at all the same as connect-and-resume. conduit has always been able to do what you mention, without BufferedSource:
source $$ (sink1 >> sink2)
The difference with a BufferedSource is that you can run a bunch of arbitrary code inside. I posted elsewhere a more in-depth explanation of the webserver example. Another use case is simplifying interleaving of sources.
[–]drb226 4 points5 points (0 children)
sorry, this has been archived and can no longer be voted on
Here's hoping that pipes and conduit will continue to have a mutually-beneficial relationship! In the end, I think our main goal should be to either 1) merge the two packages, or 2) draw a clear line between the two. That line used to be practicality vs theory, but I find it highly likely that a thoroughly thought out theory will end up being the most practical solution on all accounts.
It's amazing how many phases of evolution conduits have been through in such a short time period, and I don't think it's an overstatement to say that the package has been showered with praise every step of the way. I again feel that this is a good step forward, and eagerly anticipate the next development.
[–]snoyberg[S] 3 points4 points (9 children)
sorry, this has been archived and can no longer be voted on
Alright everyone, I'd like to make the BufferedSource thing a bit more concrete, and hopefully get some good input on something. I just did an initial port of Warp to conduit 0.4. As I expected, the tricky bit was coming up with a way to handle the request body. What we want is:
• Get a Source from the Socket.
• Parse the request headers from that Source, holding onto any leftover input.
• Let the application parse the request body. It should be able to parse the leftover input, but should not be allowed to consume more than content-length bytes.
• After the application finishes, Warp should flush the Source for any remaining bytes not consumed from the RequestBody, but should not consume any other bytes, since they may be part of a pipelined request.
I believe that this will necessitate some kind of mutable variable, since we need to know how many bytes the application consumed, but the application won't be telling us that. My solution was to create an IsolatedBSSource. It keeps track of how many bytes can still be consumed downstream by the application, and the most recent Source. It uses the new connect-and-resume operator to grab the next chunk and then get an updated Source.
We have a fairly thorough set of tests covering the pipelining and request body behavior, so I feel fairly confident that the code is doing the right thing. I'm wondering if anyone has ideas on better approaches. Also, maybe looking at this code will explain why BufferedSource was such a fundamental design decision in conduit from the beginning.
[–]pcapriotti 1 point2 points (2 children)
sorry, this has been archived and can no longer be voted on
I helped implementing a proof of concept http server with pipes, and the approach I used was to define a "sequencer" pipe that keeps composing handlers to handle pipelined requests. Here is a sketch: https://gist.github.com/1809002.
With this approach, the handler (i.e. the application) is a Pipe itself, reading input data from the request body, and writing data into the response body.
[–]snoyberg[S] 1 point2 points (1 child)
sorry, this has been archived and can no longer be voted on
And that's exactly what we want to avoid. We went down that route with enumerator, and it introduces far too many complications. It becomes difficult to deal with exceptions (since Pipe can't be an instance of MonadBaseControl IO), and implementing something like an HTTP proxy is virtually impossible
[–]pcapriotti 1 point2 points (0 children)
sorry, this has been archived and can no longer be voted on
I think it's either that or "resumable" pipelines via mutable state, like you said.
I personally prefer the approach of just composing pipes to express the desired behavior, for the usual reasons why mutable state is bad.
Note that you can do exception handling in pipes-core as if Pipe were an instance of MonadBaseControl, as you have the same primitives of lifted-base.
[–]apfelmus 1 point2 points (4 children)
sorry, this has been archived and can no longer be voted on
A small note concerning the original BufferredSource:
Reading the example code in your blog post, I think that BufferedSource has a fundamental flaw, namely the following:
Ignoring resource management, you can think of sources as representing a list of input characters. With that point of view, the code
bsrc <- bufferSource $ sourceSocket socket
headers <- bsrc $$ getHeaders
let req = makeRequest headers bsrc
app req
looks as if you are taking a single list of characters bsrc and parse it twice, once via getHeaders and once via makeRequest. But that's not what happens, the call to getHeadres will mutate the contents of the list, namely remove the header. Obviously, that's a side effect.
In constrast, your second variant returns a new "list" src2 and no side effects are needed to describe what elements it contains. I think that's a clear advantage of your new approach.
[–]snoyberg[S] 1 point2 points (3 children)
sorry, this has been archived and can no longer be voted on
What you're saying is absolutely true, and is why I prefer the new approach more. However, the mutate-the-source approach is exactly how most non-conduit data sources work (e.g., Handle, Socket).
[–]apfelmus 2 points3 points (2 children)
sorry, this has been archived and can no longer be voted on
Actually, the more I think about it, the more the treatment of sources as first-class values (that you can pass around and so on) appears to me as a radical departure from the original goal of iteratees.
The thing is this: whenever you can get your hands on a first-class value, like src or src2, you can duplicate it. Nobody can stop you from using, say src1 twice
let src1 = sourceSocket socket
(src2, headers) <- src1 $$& getHeaders
let req = makeRequest headers src1
app req
You have to specify what it means to use a single source twice. There are many possibilities:
• The original Handle type treated it as a pointer, as did the BufferedSource.
• Your Source type treated it as single-use, it will already be closed the second time.
• Both variants above depend on side effects. The only pure way is the "list of characters" point of view treats it as a single list. That works for hard drive access, you can always reopen a file and close it again. But for network connections, you would have to store them, just in case they are used twice. Soon enough, you will need to perform garbage collection.
If you want to make sure that a source is used in a single-threaded fashion, the only way to do that is to "bake it into the combinators". As others have mentioned, "the right thing" to do is to write makeRequest as a pipe
makeRequest :: Headers -> Pipe Word8 ...
let src = sourceSocket socket
req <- src $$ (getHeaders >>= makeRequest)
app req
instead of
makeRequest :: Headers -> Source -> ...
If you don't want to do that, then you have to think about how duplication affects resource management, something that iteratees were made to avoid by baking the Handle into the combinators.
[–]snoyberg[S] 1 point2 points (1 child)
sorry, this has been archived and can no longer be voted on
You're right: this is one of the major things we're trying to change from enumerator, because forcing us to do "the right thing" you refer to turned out to be very bad in practice. I'd like to emphasize two points here:
• You make it sound like reusing a Source is a new problem that conduit introduced. That's not true: you could just as easily have done the same thing in enumerator, and I presume in pipes too:
let src = enumSocket socket
headers <- src $$ getHeaders
let req = makeRequest headers src
• The code you're referring to is bad, but it's explicitly mentioned as one of the invariants of conduit. I consider the connect-and-resume approach low-level, and as such it's a bit dangerous. (It also doesn't clean up resources automatically by the way.) But sometimes, we need low-level tools like this.
So yes: if someone wanted to write the code you mention above, they would need to think long and hard about what it means.[1] But doing so is using the library the wrong way.
[1] I can tell you right now by the way: the second time src1 is used, it would pull the next chunk of data from the socket, ignoring any leftover data provided by getHeaders.
[–]apfelmus 0 points1 point (0 children)
sorry, this has been archived and can no longer be voted on
Ah, right, the issue has always been there for iteratees as well.
Hm, I do think that there is something more to this story, but I can't quite put my finger on it. In any case, the way you handle it is ok, I think.
[–]phischu 0 points1 point (0 children)
sorry, this has been archived and can no longer be voted on
I wrote a small demonstration that should fit your specification. The important parts:
getHeader :: Pipe ByteString ByteString IO (Header,ByteString)
webserver :: Pipe ByteString ByteString IO a -> Pipe ByteString ByteString IO ()
webserver app = do
(header,rest) <- getHeader
cons rest >+> (take (requestSize header) >> return ()) >+> (app >> discard)
cons :: (Monad m) => a -> Pipe a a m r
cons x = yield x >> idP
getHeader returns the parsed Header as well as the unparsed rest. cons feeds that rest to the next pipe and then acts like the identity pipe. take together with discard ensures that exactlyrequestSize header bytes are read and then the pipe terminates. The return () makes explicit that if the last chunk of the request body contains parts of the next request they are discarded.
You said that you don't want your request handler to be a pipe. What else should it be? Can that be lifted into a pipe?
[–]phischu 1 point2 points (3 children)
sorry, this has been archived and can no longer be voted on
It is probably a very stupid question but why not instead of
let src = sourceSocket socket
headers <- src $$ getHeaders
let req = makeRequest headers src
app req
something like this
let src = sourceSocket socket
let req = src $$ (getHeaders >>= makeRequest)
app req
It probably won't work exactly like this, but as far as I understand there are two ways to compose pipes. (&&) is for pumping the output stream of one pipe into another one and (>>=) lets a pipe pick up where the previous one left off.
[–]snoyberg[S] 2 points3 points (2 children)
sorry, this has been archived and can no longer be voted on
The types don't even add up there. The type for req would now be IO Request, so presumably Application would be IO Request -> IO Response. As soon as you run the action to get your Request, the data discarding has already occurred.
[–]Axman6 1 point2 points (1 child)
sorry, this has been archived and can no longer be voted on
Hmm, I'm confused now. I had always assumed that I could do something like:
src $$ (do
x <- consumesSome
y <- consumesSomeMore x
consumesTheRest x y
)
Is this not the case? I believe Enumeratee let you do things like that.
On another note, are there any benchmarks for this new implementation of Conduit? I understand quite well that one thing that iteratee code should be is fast (at least when using a pragmatic package like Conduit, others might have other goals).
I also wonder what effect moving to a single type has on type errors given to the user. It seems to be you had a good point that the error messages may be clearer when using the three types. I guess the new type idea is not a bad one, it keeps the type safety we want, hopefully makes the type errors more obvious, and adds no additional overhead to the runtime (only to the low level programmer, and this could easily be avoided with smart constructors).
Thanks for all your hard work Micheal, I'm always appreciative of your work to build powerful, useful, and high performance libraries in Haskell. If only the mathematicians would keep their noses out =)
[–]snoyberg[S] 2 points3 points (0 children)
sorry, this has been archived and can no longer be voted on
You're correct: Sinks can be composed monadically exactly the way you describe. The problem is when consumesSomeMore is really a massive function (like a web application) that will be performing a bunch of other code, and eventually read in the request body.
Under enumerator-based WAI, the solution was to have the application live in the Iteratee monad (equivalent to Sink). For various reasons, this greatly complicates things. (Mostly exception handling. But I'm kind of invoking proof-by-assertion here, just trust me that it was bad.)
Also, the error message issue is my biggest concern right now with the unified type.
[–]donri 1 point2 points (1 child)
sorry, this has been archived and can no longer be voted on
Did you try making your Pipe a Category?
[–]snoyberg[S] 1 point2 points (0 children)
sorry, this has been archived and can no longer be voted on
No, not yet.
[–]simonmar 1 point2 points (1 child)
sorry, this has been archived and can no longer be voted on
typo in docs for the Pipe type: "This is due to the fact that any result produced by the left pipe must be discarded in favor of the left pipe."
[–]snoyberg[S] 1 point2 points (0 children)
sorry, this has been archived and can no longer be voted on
Thanks, fixed.
[–]IdolfHatler 1 point2 points (7 children)
sorry, this has been archived and can no longer be voted on
I really liked the changes done in conduit 0.30. I think all the constructors are fairly simple and the types seems to match the use cases. As far as I can tell you only need to know the two invariants to be able to use (low-level) library - never reuse and do not yield data you have not received.
Overall I think they are the simplest to understand of all the versions so far. They are a bit inconsistent though - Source m a, Conduit input m output, Sink input m output. Wouldn't it make more sense to use Source m output, Conduit input m output, Sink input m result? I have a similar complaint for their constructors - but this is all very minor details! ;)
I like the new change from BufferedSource to a resumable operator. It gives rise to a bit more boilerplate, however the main invariant is never relaxed in this case, leading to simpler understanding for people who are new to the library and leading to a simpler interface for the programmer.
However I don't like the combination of Sink, Source and Conduit into a single type. For example it would be possible to construct a Source that needs input (of unit type) - or perhaps even worse a "closed" conduit that still needs input. Likewise you could construct a Sink that that has output. So you would now need invariants for stuff that was forced by the type system before.
Of course this is a reasonable compromise if the change leads to other benefits however I cannot see such benefits currently.
Though this new Pipe is fairly simple, I do not find it as simple to use in practice as the Source, Sink and Conduit types. I would need to know in much in much more detail what a pipe is allowed and not allowed to do, thus making it harder to write code around the types.
For example, when I use the "closed" pipe from a NeedInput pipe, I still need to handle the case where the returned pipe is a NeedInput too - unless I want to get a "Pattern match(es) are non-exhaustive". In this case it should probably be handled with an error, but I still need to keep track of that in my head. :)
/my two cents
[–]ehird 2 points3 points (6 children)
sorry, this has been archived and can no longer be voted on
However I don't like the combination of Sink, Source and Conduit into a single type. For example it would be possible to construct a Source that needs input (of unit type) - or perhaps even worse a "closed" conduit that still needs input. Likewise you could construct a Sink that that has output. So you would now need invariants for stuff that was forced by the type system before.
This is untrue. Since the output parameter for Sink is set to Void, it is impossible for it to yield any data (without resorting to undefined). And since the input parameter for Source is Void, you know (since there are no values of Void) that the output-only pipe you specify is the branch that will be taken, i.e. it's guaranteed to only receive an empty stream.
When a Sink claims to output, the correct thing to do is to use absurd :: Void -> a on the Void value it purports to give you; when a Source wants input, the correct thing to do is to tell it there's none. (This is actually an advantage, since you can use pipes which can use input but don't need it as sources.)
[–]snoyberg[S] 0 points1 point (0 children)
sorry, this has been archived and can no longer be voted on
I think you're both correct. My understanding of @IdolfHatler is that, even though we know that the HaveOutput constructor can never exist for a Sink, we still have to deal with it (assuming we want to avoid GHC warnings about unmatched patterns, which I think is good coding practice). It's completely true that absurd proves that there's nothing to worry about, but the need to write out that case is a disadvantage.
Whether it's a large enough disadvantage to avoid combining the types is- I believe- the question on the table.
[–]IdolfHatler 0 points1 point (2 children)
sorry, this has been archived and can no longer be voted on
In the documentation the type is not Void, but (). I see that has been changed.
Do you not still need to pattern match for those constructors? Also, will this change alter the invariants?
[–]ehird 1 point2 points (1 child)
sorry, this has been archived and can no longer be voted on
Do you not still need to pattern match for those constructors?
Yes, but the majority of code won't have to pattern-match on the constructors at all, just like before. And, since you don't have to write the same algorithm three times (for sources, sinks and conduits), it's actually less code in the end.
Also, will this change alter the invariants?
I don't think so, but I'm not sure exactly which invariants you're referring to.
[–]IdolfHatler 1 point2 points (0 children)
sorry, this has been archived and can no longer be voted on
You are right, that you would probably never pattern match if you were using the high level API - but I don't think you would be using the constructors itself or the Pipe-type much either. So in this case I don't really think it matters which version you choose. Thus I mainly focus on writing/reading low-level code.
Version 0.30 of the conduit library had very few rules for what a source/sink/conduit was allowed to do and not do - you cannot reuse them (except for BufferedSource, which I think should be removed anyways) and a sink/counduit could not yield data that had not been supplied to it.
This change introduced more rules to keep track of, such as a Sink can never use the HaveOutput constructor. Before this was not possible at all, since it did not exist - but now it is possible (by using undefined), and if you are to pattern match on unless you want a GHC warning and you should treat it as an error of the pattern actually matches. Thus you have introduced more rules for using the library properly.
If the goal of this change is to simplify how easy it is to understand the low-level API, then my opinion is that I think it has failed to do so.
You might be right that the change leads to less code duplication and feel that it is a fair compromise - I have not yet formed an opinion on that subject. My only argument is that in my opinion the change is a complication of the datatypes themselves, not a simplification.
[–]IdolfHatler 0 points1 point (1 child)
sorry, this has been archived and can no longer be voted on
Also, I do not see how it is an advantage to have a source that can take an input, but does not need it. You could do that before with a conduit.
[–]ehird 0 points1 point (0 children)
sorry, this has been archived and can no longer be voted on
Well, I'm just saying that there's no reason to separate the concepts: a Source is just a conduit that can't be supplied input.
[–]DannoHung 0 points1 point (0 children)
sorry, this has been archived and can no longer be voted on
The Hackage link to the conduits page is broken: Missing the trailing s
[–]sseveran 0 points1 point (6 children)
sorry, this has been archived and can no longer be voted on
I have a few comments on the whole discussion surrounding conduits/pipes etc… My comments come from someone who has started a company that uses haskell for most of its codebase.
From strictly what can I build perspective there doesn’t seem to be significant differences between iteratee/enumerator/conduit/etc… I may not fully appreciate the limitations of some of these libraries and it may not be equally easy to implement a certain piece of functionality across these libraries. I understand Michael’s motivations for conduit around resources and so conduit seems to be an incremental step forward.
I am not sure what the objective of the pipes packages is over offering a different API. Without API testing I don’t know how people can claim that one API is superior to another strictly from an ease of use perspective. As a user, these packages simply seem to be the same thing again with a different API. There are now at least six packages that claim to be the library for streaming data.
At some point as a community we need to decide what we want. As someone who has to maintain a codebase for a living I value API stability. Others may have different motivations. Its good that the community is having a discussion about this but I would hope that the various package implementers would keep in mind that it is useful to articulate what real world problems their changes are solving. At this point I don’t see any real advantage to any library except conduit, because conduit solved some real world issues. I understand that some similar functionality is forthcoming for iteratee.
My comments on the various proposals:
I like the idea of a single combining operator if that is possible. It would need to preserve good error messages, which I would suspect would be difficult to impossible.
Removing BufferedSource is fine so long as there is a replacement with the same functionality. While it may not be elegant it does fix problems that were not convenient to implement in enumerator.
I like the Source, Conduit, Sink as it contributes to readability and they are likely to generate error messages in the type checker that are clearer. IMHO this will help new users to the library more than most anything else.
The specific operator to combine them doesn’t seem very important. What they are today seems fine and anything different is likely to just be a style choice.
In conclusion I don’t feel too strongly about any specific implementation but if we are going to make changes lets make sure we are getting significant value for them.
[–]cdsmith 9 points10 points (2 children)
sorry, this has been archived and can no longer be voted on
At some point as a community we need to decide what we want. As someone who has to maintain a codebase for a living I value API stability.
Let me provide the counterpoint to that.
Haskell is what it is today because people are willing to rethink things. You are, after all, choosing to use a programming language where it took literally years of debating multiple designs to answer the question of "how do we print Hello World?" And even that is still occasionally debated to this day.
Haskell is also what it is today because people are willing to think formally about semantics, and not just throw in whatever solves the specific problems they are facing right now. As a community, we look for ways to build software that satisfies expected laws of behavior, and matches the meaning expressed by simple well-described models. That's led to some really good things, and we have a better programming language for it.
Not to say there isn't a trade-off here. Stability in the really basic parts of the Haskell library ecosystem is valuable, sure, and we're getting there. But the conduit library is less than three months old, and on version 0.3 now! If you're really that worried about breaking API changes in a pre-1.0 library version that has only been around for a couple of months, then I'd suggest maybe you misunderstand the basic dynamics of the community.
[–]sseveran 1 point2 points (1 child)
sorry, this has been archived and can no longer be voted on
I don't disagree. Due to the number of other packages I use that depend on conduit, it is rapidly becoming a core package. However in practice managing all these dependencies is a bit more complicated and it is often necessary to port code due to the butterfly problem or more commonly not upgrade at all. In practice when I am able I try to stay on a stable package set that we upgrade twice a year.
I don't mind breaking changes very much so long as the changes are giving a demonstrable value. I am simply observing that as someone usually on the outside of these discussions there are many sets of semantics that work and measuring objectively whether one set is better than another is quite difficult and will usually be subjective. From working the conduit APIs so far I don't think of it as better or worse than enumerator, mostly just different. In time this may be different and I am certainly happy that people are trying out new ideas (one of the good things about this community). I like the idea of a discussion around these problems as I think it would be good to avoid needing a new library to address unforeseen problems again. I would suggest that I care a lot less about which operators get picked then how thorny issues like error handling work.
I look forward to the rest of this spirited discussion.
[–]snoyberg[S] 2 points3 points (0 children)
sorry, this has been archived and can no longer be voted on
I would agree that, from a user of Warp or http-conduit/-enumerator, there's not much of a difference between enumerator and conduit. I don't really intend conduit to be a package used by most programs for most tasks. For example, if you look through the Yesod book, I think there's only one example (besides the conduit chapter itself) that uses conduits. It's a low-level tool.
The one demonstrable change should be the greatly simplified API we were able to add to http-conduit by getting rid of the Inversion of Control necessary for enumerator. That is directly caused by the move to BufferedSource, which is why I consider it such a central concept in the library, and why I've been so dismissive of claims to "fix" conduit which don't involve it.
In other words: if you're working with xml-conduit, Warp, yaml, or any of the other few dozen packages uses conduit, I hope this discussion is completely irrelevant to you. conduit 0.0 to 0.2 introduces significant performance enhancements without modifying the external API much. It was important, but internal. 0.3 was even more internal: it simplified the API for those of us writing conduit code, but hardly touched user-facing code.
If this set of changes goes through for 0.4 (which is not a given), it will be even less intrusive than the 0.3 changes. In my testing so far, all that really needs to change is the names of constructors in your code.
I agree that as a community it would be great to standardize on just a single package. I tried for a while to make that package enumerator, but unfortunately for various reasons it wasn't possible. I feel pretty confident in conduit and its ability to solve our problems. Time will tell if the rest of the community agrees with me.
[–]illissius 2 points3 points (1 child)
sorry, this has been archived and can no longer be voted on
This is just my superficial impression, but I think the right order of things is
1. Thoroughly explore the design space, find out what the options and tradeoffs are
2. Figure out which option is the best one
3. Standardize on it
and it very much feels like we're still somewhere in 1/2.
[–]pcapriotti 5 points6 points (0 children)
sorry, this has been archived and can no longer be voted on
I agree. Also, releasing a library to hackage doesn't imply any claim that the library is usable for production code or is the best possibly solution to its use cases.
It's unfortunate that hackage gets polluted over time with failed attempts and deprecated libraries, but I don't think this problem should be solved by discouraging people from releasing experimental approaches.
[–]Axman6 0 points1 point (0 children)
sorry, this has been archived and can no longer be voted on
This was exactly my problem with the initial post, which almost felt like it was preaching some magical solution to all of our problems, without addressing any of the main motivations behind Conduit. Michael understands the issues you're having in the real world, and this is why he's made many of the decisions he has. Some of these solutions could be more elegant, but there's often a good reason for them not to be so in the long run.
|
{
"url": "http://www.reddit.com/r/haskell/comments/reft1/pipeslike_conduit/",
"source_domain": "www.reddit.com",
"snapshot_id": "crawl=CC-MAIN-2015-22",
"warc_metadata": {
"Content-Length": "287943",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:VVRYRSUD2SAB5WVSYLYEAUJDOEGV5GJ2",
"WARC-Concurrent-To": "<urn:uuid:75a71fa1-1387-44e6-af96-3e98792f1619>",
"WARC-Date": "2015-05-29T08:27:35Z",
"WARC-IP-Address": "198.41.209.142",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:XSLCJKLZ5PSWFCNXOKKASYSEIOW2SDC6",
"WARC-Record-ID": "<urn:uuid:368a5642-0edc-4ff8-818c-856a75d3a98f>",
"WARC-Target-URI": "http://www.reddit.com/r/haskell/comments/reft1/pipeslike_conduit/",
"WARC-Truncated": "length",
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:ae615b52-95a3-40f7-b331-94c9c305690e>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-180-206-219.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2015-22\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web for May 2015\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
16,
17,
59,
60,
120,
121,
134,
135,
254,
255,
870,
871,
1247,
1248,
1931,
1932,
2221,
2222,
2743,
2744,
3644,
3645,
3744,
3745,
3862,
3863,
3940,
3995,
4055,
4110,
4175,
4196,
4205,
4239,
4262,
4263,
4387,
4388,
4434,
4435,
4495,
4496,
4678,
4679,
4916,
4917,
5269,
5270,
5310,
5311,
5371,
5372,
5481,
5482,
5521,
5522,
5582,
5583,
5820,
5821,
5941,
5942,
6135,
6136,
6176,
6177,
6237,
6238,
6268,
6269,
6307,
6308,
6357,
6358,
6395,
6396,
6456,
6457,
6728,
6729,
6775,
6776,
6836,
6837,
7183,
7184,
7226,
7227,
7287,
7288,
7389,
7390,
7446,
7447,
7484,
7485,
7614,
7615,
7647,
7648,
7710,
7766,
7767,
7862,
7863,
7909,
7910,
7970,
7971,
8152,
8153,
8193,
8194,
8254,
8255,
8522,
8523,
8598,
8599,
8644,
8645,
8705,
8706,
8844,
8845,
8884,
8885,
8945,
8946,
9172,
9173,
9212,
9213,
9273,
9274,
9521,
9522,
9637,
9638,
9677,
9678,
9738,
9739,
9816,
9817,
9935,
9936,
10175,
10176,
10216,
10217,
10277,
10278,
10552,
10553,
10808,
10809,
10851,
10852,
10912,
10913,
11115,
11116,
11184,
11185,
11224,
11225,
11285,
11286,
11411,
11412,
11546,
11547,
11590,
11591,
11651,
11652,
11931,
11932,
12172,
12173,
12197,
12198,
12310,
12311,
12356,
12357,
12417,
12418,
12438,
12439,
12694,
12695,
12990,
12991,
13221,
13222,
13301,
13302,
13344,
13345,
13405,
13406,
13631,
13632,
13677,
13678,
13738,
13739,
13944,
13945,
14197,
14198,
14240,
14241,
14301,
14302,
14496,
14497,
14694,
14695,
14740,
14741,
14801,
14802,
15179,
15180,
15323,
15324,
15368,
15369,
15429,
15430,
15530,
15531,
15677,
15678,
16001,
16002,
16216,
16217,
16259,
16260,
16320,
16321,
16762,
16763,
16861,
16862,
16907,
16908,
16968,
16969,
17248,
17249,
17332,
17333,
17364,
17365,
17893,
17894,
18073,
18074,
18265,
18266,
18492,
18493,
18577,
18578,
18623,
18624,
18684,
18685,
18821,
18822,
19140,
19141,
19183,
19184,
19244,
19245,
19377,
19378,
19431,
19453,
19454,
19493,
19494,
19537,
19570,
19571,
19709,
19710,
19755,
19756,
19900,
19901,
19930,
19954,
19967,
19968,
20160,
20161,
20202,
20245,
20293,
20294,
20395,
20396,
20439,
20440,
20500,
20501,
20643,
20644,
20879,
20880,
20974,
20975,
21019,
21020,
21080,
21081,
21391,
21392,
21438,
21439,
21499,
21500,
21893,
21894,
22093,
22094,
22134,
22135,
22195,
22196,
22846,
22847,
23243,
23244,
23290,
23291,
23351,
23352,
23683,
23684,
23726,
23727,
23787,
23788,
24272,
24273,
24319,
24320,
24380,
24381,
24490,
24491,
24530,
24531,
24591,
24592,
24648,
24649,
24690,
24691,
24751,
24752,
25137,
25138,
25177,
25178,
25238,
25239,
25472,
25473,
25514,
25515,
25575,
25576,
25783,
25784,
25834,
25884,
25922,
25923,
26209,
26210,
26234,
26258,
26294,
26295,
26662,
26663,
26701,
26702,
26762,
26763,
27178,
27179,
27246,
27247,
27286,
27287,
27347,
27348,
27616,
27617,
27631,
27645,
27646,
27711,
27712,
27766,
27767,
27803,
27804,
27840,
27841,
27901,
27902,
27927,
27928,
27969,
27970,
28030,
28031,
28188,
28189,
28234,
28235,
28295,
28296,
28442,
28443,
28654,
28655,
28695,
28696,
28756,
28757,
29213,
29214,
29503,
29504,
29847,
29848,
29931,
29932,
30017,
30018,
30106,
30107,
30198,
30199,
30507,
30508,
30823,
30824,
31542,
31543,
31588,
31589,
31649,
31650,
31920,
31921,
32366,
32367,
32646,
32647,
33318,
33319,
33355,
33356,
33416,
33417,
33477,
33478,
33506,
33507,
33552,
33553,
33613,
33614,
33751,
33752,
33779,
33780,
34001,
34002,
34043,
34044,
34104,
34105,
34495,
34496,
34803,
34804,
34850,
34851,
34911,
34912,
35192,
35193,
35227,
35308,
35472,
35683,
35684,
36121,
36122,
36470,
36471,
36515,
36516,
36576,
36577,
36810,
36811,
36967,
36968,
37010,
37011,
37071,
37072,
37374,
37375,
37419,
37420,
37480,
37481,
37565,
37566,
37704,
37705,
37856,
37857,
37899,
37900,
37960,
37961,
38015,
38016,
38134,
38135,
38268,
38269,
38312,
38342,
38377,
38385,
38386,
38661,
38662,
38847,
38848,
38893,
38894,
38954,
38955,
39151,
39152,
39195,
39196,
39256,
39257,
39461,
39462,
39624,
39625,
39656,
39695,
39730,
39738,
39739,
39833,
39834,
39915,
40005,
40375,
40376,
40599,
40600,
40641,
40642,
40672,
40715,
40723,
40724,
40735,
40736,
40776,
40777,
40968,
40969,
41011,
41012,
41072,
41073,
41293,
41294,
41490,
41491,
41524,
41558,
41597,
41602,
41911,
41912,
42087,
42088,
42264,
42265,
42307,
42308,
42368,
42369,
42435,
42436,
42585,
42586,
42627,
42628,
42688,
42689,
42776,
42777,
42840,
42841,
42922,
42941,
42972,
43052,
43053,
43092,
43116,
43117,
43497,
43498,
43618,
43619,
43660,
43661,
43721,
43722,
43783,
43784,
43814,
43843,
43877,
43885,
43886,
43906,
43907,
43937,
43983,
43991,
43992,
44228,
44229,
44275,
44276,
44336,
44337,
44569,
44570,
44607,
44608,
44668,
44669,
44745,
44746,
44757,
44779,
44807,
44831,
44833,
44834,
44906,
44907,
45152,
45153,
45609,
45610,
45813,
45814,
45860,
45861,
45921,
45922,
46181,
46182,
46464,
46465,
46550,
46551,
46587,
46588,
46648,
46649,
46690,
46691,
46736,
46737,
46797,
46798,
46811,
46812,
46851,
46852,
46912,
46913,
47058,
47059,
47104,
47105,
47165,
47166,
47181,
47182,
47227,
47228,
47288,
47289,
47588,
47589,
47951,
47952,
48244,
48245,
48628,
48629,
48755,
48756,
49029,
49030,
49347,
49348,
49362,
49363,
49403,
49404,
49464,
49465,
49848,
49849,
50214,
50215,
50528,
50529,
50574,
50575,
50635,
50636,
51055,
51056,
51168,
51169,
51214,
51215,
51275,
51276,
51356,
51357,
51465,
51466,
51502,
51503,
51563,
51564,
51627,
51628,
51869,
51870,
51915,
51916,
51997,
51998,
52043,
52044,
52104,
52105,
52423,
52424,
52707,
52708,
53126,
53127,
53273,
53274,
53549,
53550,
53592,
53593,
53653,
53654,
53800,
53801,
53840,
53841,
53901,
53902,
54030,
54031,
54074,
54075,
54135,
54136,
54208,
54209,
54251,
54252,
54312,
54313,
54491,
54492,
54916,
54917,
55310,
55311,
55906,
55907,
55945,
55946,
56117,
56118,
56315,
56316,
56542,
56543,
56701,
56702,
56870,
56871,
56914,
56915,
56975,
56976,
57115,
57116,
57157,
57158,
57464,
57465,
57896,
57897,
58344,
58345,
58384,
58385,
58445,
58446,
58847,
58848,
59712,
59713,
59769,
59770,
59816,
59817,
59877,
59878,
60258,
60259,
60633,
60634,
61072,
61073,
61291,
61292,
61624,
61625,
61666,
61667,
61727,
61728,
61809,
61810,
61896,
61941,
61964,
61965,
62023,
62024,
62069,
62070,
62130,
62131,
62299,
62300,
62512,
62513,
62553,
62554,
62614,
62615
],
"line_end_idx": [
16,
17,
59,
60,
120,
121,
134,
135,
254,
255,
870,
871,
1247,
1248,
1931,
1932,
2221,
2222,
2743,
2744,
3644,
3645,
3744,
3745,
3862,
3863,
3940,
3995,
4055,
4110,
4175,
4196,
4205,
4239,
4262,
4263,
4387,
4388,
4434,
4435,
4495,
4496,
4678,
4679,
4916,
4917,
5269,
5270,
5310,
5311,
5371,
5372,
5481,
5482,
5521,
5522,
5582,
5583,
5820,
5821,
5941,
5942,
6135,
6136,
6176,
6177,
6237,
6238,
6268,
6269,
6307,
6308,
6357,
6358,
6395,
6396,
6456,
6457,
6728,
6729,
6775,
6776,
6836,
6837,
7183,
7184,
7226,
7227,
7287,
7288,
7389,
7390,
7446,
7447,
7484,
7485,
7614,
7615,
7647,
7648,
7710,
7766,
7767,
7862,
7863,
7909,
7910,
7970,
7971,
8152,
8153,
8193,
8194,
8254,
8255,
8522,
8523,
8598,
8599,
8644,
8645,
8705,
8706,
8844,
8845,
8884,
8885,
8945,
8946,
9172,
9173,
9212,
9213,
9273,
9274,
9521,
9522,
9637,
9638,
9677,
9678,
9738,
9739,
9816,
9817,
9935,
9936,
10175,
10176,
10216,
10217,
10277,
10278,
10552,
10553,
10808,
10809,
10851,
10852,
10912,
10913,
11115,
11116,
11184,
11185,
11224,
11225,
11285,
11286,
11411,
11412,
11546,
11547,
11590,
11591,
11651,
11652,
11931,
11932,
12172,
12173,
12197,
12198,
12310,
12311,
12356,
12357,
12417,
12418,
12438,
12439,
12694,
12695,
12990,
12991,
13221,
13222,
13301,
13302,
13344,
13345,
13405,
13406,
13631,
13632,
13677,
13678,
13738,
13739,
13944,
13945,
14197,
14198,
14240,
14241,
14301,
14302,
14496,
14497,
14694,
14695,
14740,
14741,
14801,
14802,
15179,
15180,
15323,
15324,
15368,
15369,
15429,
15430,
15530,
15531,
15677,
15678,
16001,
16002,
16216,
16217,
16259,
16260,
16320,
16321,
16762,
16763,
16861,
16862,
16907,
16908,
16968,
16969,
17248,
17249,
17332,
17333,
17364,
17365,
17893,
17894,
18073,
18074,
18265,
18266,
18492,
18493,
18577,
18578,
18623,
18624,
18684,
18685,
18821,
18822,
19140,
19141,
19183,
19184,
19244,
19245,
19377,
19378,
19431,
19453,
19454,
19493,
19494,
19537,
19570,
19571,
19709,
19710,
19755,
19756,
19900,
19901,
19930,
19954,
19967,
19968,
20160,
20161,
20202,
20245,
20293,
20294,
20395,
20396,
20439,
20440,
20500,
20501,
20643,
20644,
20879,
20880,
20974,
20975,
21019,
21020,
21080,
21081,
21391,
21392,
21438,
21439,
21499,
21500,
21893,
21894,
22093,
22094,
22134,
22135,
22195,
22196,
22846,
22847,
23243,
23244,
23290,
23291,
23351,
23352,
23683,
23684,
23726,
23727,
23787,
23788,
24272,
24273,
24319,
24320,
24380,
24381,
24490,
24491,
24530,
24531,
24591,
24592,
24648,
24649,
24690,
24691,
24751,
24752,
25137,
25138,
25177,
25178,
25238,
25239,
25472,
25473,
25514,
25515,
25575,
25576,
25783,
25784,
25834,
25884,
25922,
25923,
26209,
26210,
26234,
26258,
26294,
26295,
26662,
26663,
26701,
26702,
26762,
26763,
27178,
27179,
27246,
27247,
27286,
27287,
27347,
27348,
27616,
27617,
27631,
27645,
27646,
27711,
27712,
27766,
27767,
27803,
27804,
27840,
27841,
27901,
27902,
27927,
27928,
27969,
27970,
28030,
28031,
28188,
28189,
28234,
28235,
28295,
28296,
28442,
28443,
28654,
28655,
28695,
28696,
28756,
28757,
29213,
29214,
29503,
29504,
29847,
29848,
29931,
29932,
30017,
30018,
30106,
30107,
30198,
30199,
30507,
30508,
30823,
30824,
31542,
31543,
31588,
31589,
31649,
31650,
31920,
31921,
32366,
32367,
32646,
32647,
33318,
33319,
33355,
33356,
33416,
33417,
33477,
33478,
33506,
33507,
33552,
33553,
33613,
33614,
33751,
33752,
33779,
33780,
34001,
34002,
34043,
34044,
34104,
34105,
34495,
34496,
34803,
34804,
34850,
34851,
34911,
34912,
35192,
35193,
35227,
35308,
35472,
35683,
35684,
36121,
36122,
36470,
36471,
36515,
36516,
36576,
36577,
36810,
36811,
36967,
36968,
37010,
37011,
37071,
37072,
37374,
37375,
37419,
37420,
37480,
37481,
37565,
37566,
37704,
37705,
37856,
37857,
37899,
37900,
37960,
37961,
38015,
38016,
38134,
38135,
38268,
38269,
38312,
38342,
38377,
38385,
38386,
38661,
38662,
38847,
38848,
38893,
38894,
38954,
38955,
39151,
39152,
39195,
39196,
39256,
39257,
39461,
39462,
39624,
39625,
39656,
39695,
39730,
39738,
39739,
39833,
39834,
39915,
40005,
40375,
40376,
40599,
40600,
40641,
40642,
40672,
40715,
40723,
40724,
40735,
40736,
40776,
40777,
40968,
40969,
41011,
41012,
41072,
41073,
41293,
41294,
41490,
41491,
41524,
41558,
41597,
41602,
41911,
41912,
42087,
42088,
42264,
42265,
42307,
42308,
42368,
42369,
42435,
42436,
42585,
42586,
42627,
42628,
42688,
42689,
42776,
42777,
42840,
42841,
42922,
42941,
42972,
43052,
43053,
43092,
43116,
43117,
43497,
43498,
43618,
43619,
43660,
43661,
43721,
43722,
43783,
43784,
43814,
43843,
43877,
43885,
43886,
43906,
43907,
43937,
43983,
43991,
43992,
44228,
44229,
44275,
44276,
44336,
44337,
44569,
44570,
44607,
44608,
44668,
44669,
44745,
44746,
44757,
44779,
44807,
44831,
44833,
44834,
44906,
44907,
45152,
45153,
45609,
45610,
45813,
45814,
45860,
45861,
45921,
45922,
46181,
46182,
46464,
46465,
46550,
46551,
46587,
46588,
46648,
46649,
46690,
46691,
46736,
46737,
46797,
46798,
46811,
46812,
46851,
46852,
46912,
46913,
47058,
47059,
47104,
47105,
47165,
47166,
47181,
47182,
47227,
47228,
47288,
47289,
47588,
47589,
47951,
47952,
48244,
48245,
48628,
48629,
48755,
48756,
49029,
49030,
49347,
49348,
49362,
49363,
49403,
49404,
49464,
49465,
49848,
49849,
50214,
50215,
50528,
50529,
50574,
50575,
50635,
50636,
51055,
51056,
51168,
51169,
51214,
51215,
51275,
51276,
51356,
51357,
51465,
51466,
51502,
51503,
51563,
51564,
51627,
51628,
51869,
51870,
51915,
51916,
51997,
51998,
52043,
52044,
52104,
52105,
52423,
52424,
52707,
52708,
53126,
53127,
53273,
53274,
53549,
53550,
53592,
53593,
53653,
53654,
53800,
53801,
53840,
53841,
53901,
53902,
54030,
54031,
54074,
54075,
54135,
54136,
54208,
54209,
54251,
54252,
54312,
54313,
54491,
54492,
54916,
54917,
55310,
55311,
55906,
55907,
55945,
55946,
56117,
56118,
56315,
56316,
56542,
56543,
56701,
56702,
56870,
56871,
56914,
56915,
56975,
56976,
57115,
57116,
57157,
57158,
57464,
57465,
57896,
57897,
58344,
58345,
58384,
58385,
58445,
58446,
58847,
58848,
59712,
59713,
59769,
59770,
59816,
59817,
59877,
59878,
60258,
60259,
60633,
60634,
61072,
61073,
61291,
61292,
61624,
61625,
61666,
61667,
61727,
61728,
61809,
61810,
61896,
61941,
61964,
61965,
62023,
62024,
62069,
62070,
62130,
62131,
62299,
62300,
62512,
62513,
62553,
62554,
62614,
62615,
63052
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 63052,
"ccnet_original_nlines": 898,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.4676457345485687,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.023781120777130127,
"rps_doc_frac_lines_end_with_ellipsis": 0.0022246900480240583,
"rps_doc_frac_no_alph_words": 0.17519010603427887,
"rps_doc_frac_unique_words": 0.15554532408714294,
"rps_doc_mean_word_length": 4.500230312347412,
"rps_doc_num_sentences": 517,
"rps_doc_symbol_to_word_ratio": 0.0011182300513610244,
"rps_doc_unigram_entropy": 5.989112854003906,
"rps_doc_word_count": 10865,
"rps_doc_frac_chars_dupe_10grams": 0.15850290656089783,
"rps_doc_frac_chars_dupe_5grams": 0.18521320819854736,
"rps_doc_frac_chars_dupe_6grams": 0.17382144927978516,
"rps_doc_frac_chars_dupe_7grams": 0.16924020648002625,
"rps_doc_frac_chars_dupe_8grams": 0.1636568158864975,
"rps_doc_frac_chars_dupe_9grams": 0.1636568158864975,
"rps_doc_frac_chars_top_2gram": 0.014070970006287098,
"rps_doc_frac_chars_top_3gram": 0.020370179787278175,
"rps_doc_frac_chars_top_4gram": 0.027160240337252617,
"rps_doc_books_importance": -4830.3271484375,
"rps_doc_books_importance_length_correction": -4830.3271484375,
"rps_doc_openwebtext_importance": -3160.5888671875,
"rps_doc_openwebtext_importance_length_correction": -3160.5888671875,
"rps_doc_wikipedia_importance": -2202.697265625,
"rps_doc_wikipedia_importance_length_correction": -2202.697265625
},
"fasttext": {
"dclm": 0.23904454708099365,
"english": 0.956852376461029,
"fineweb_edu_approx": 1.421932339668274,
"eai_general_math": 0.8778170943260193,
"eai_open_web_math": 0.3628855347633362,
"eai_web_code": 0.28499287366867065
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.0151",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "4",
"label": "Analyze"
},
"secondary": {
"code": "5",
"label": "Evaluate"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "5",
"label": "Comment Section"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "4",
"label": "Advanced Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "4",
"label": "Graduate/Expert Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-1,906,253,991,611,561,700
|
Instructables
mp3 frozen what to do?
plugged mp3 player to usb cord (mtp connected charging) came up on the screen now its frozen wont go back,turn off nothing
dalmond12 years ago
IF you have access to the MP3 Player through your computer when it is connected with the USB Cable, I want you to follow these instructions to fix your problem. Right click your mouse on the Icon and select "Format" do a "Quick format" on your MP3 Players memory and it'll be fine.
tyep4 years ago
Maybe look for a reset button that you have to push with a paper clip, my zen has that.
Burf4 years ago
Try connecting the MP3 player back up to your PC, if you disconnected it. Power down your PC, let it sit for a minute or so and then restart it. Sometimes, that will wake up an unresponsive player.
NachoMahma Burf4 years ago
. Shut everything down; wait a minute; turn everything on. Works on about 75% (maybe more) of computer problems. :)
orksecurity4 years ago
If that doesn't work, this will reboot most devices:
Remove the battery from the player. Short the two battery terminals to each other for a minute or so, to make sure any capacitors have a chance to bleed down. Reinstall battery, power up.
Pro
Get More Out of Instructables
Already have an Account?
close
PDF Downloads
As a Pro member, you will gain access to download any Instructable in the PDF format. You also have the ability to customize your PDF download.
Upgrade to Pro today!
|
{
"url": "http://www.instructables.com/answers/mp3-frozen-what-to-do/",
"source_domain": "www.instructables.com",
"snapshot_id": "crawl=CC-MAIN-2014-15",
"warc_metadata": {
"Content-Length": "123026",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:NCN323BRBR3IS5MPYGFFBTYZM4PAOH77",
"WARC-Concurrent-To": "<urn:uuid:b4b6218a-3bd8-4306-a9d1-effd48915313>",
"WARC-Date": "2014-04-16T13:49:34Z",
"WARC-IP-Address": "199.27.76.129",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:WSA6E5QCBRD7QIZMMXZAIBPXRHPBOLMU",
"WARC-Record-ID": "<urn:uuid:418903e3-e0b6-4f3f-a84a-448767c0360f>",
"WARC-Target-URI": "http://www.instructables.com/answers/mp3-frozen-what-to-do/",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:d21d991e-fac0-4880-901e-77080d005668>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-147-4-33.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2014-15\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web with URLs provided by Blekko for April 2014\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
14,
15,
38,
39,
162,
163,
164,
184,
466,
482,
570,
586,
784,
811,
928,
951,
1004,
1005,
1193,
1197,
1198,
1228,
1229,
1254,
1255,
1261,
1262,
1276,
1420,
1421
],
"line_end_idx": [
14,
15,
38,
39,
162,
163,
164,
184,
466,
482,
570,
586,
784,
811,
928,
951,
1004,
1005,
1193,
1197,
1198,
1228,
1229,
1254,
1255,
1261,
1262,
1276,
1420,
1421,
1442
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 1442,
"ccnet_original_nlines": 30,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.41584157943725586,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.036303628236055374,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.14191418886184692,
"rps_doc_frac_unique_words": 0.565891444683075,
"rps_doc_mean_word_length": 4.375968933105469,
"rps_doc_num_sentences": 17,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.688694000244141,
"rps_doc_word_count": 258,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.024800710380077362,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.03542957827448845,
"rps_doc_frac_chars_top_3gram": 0.017714789137244225,
"rps_doc_frac_chars_top_4gram": 0.021257750689983368,
"rps_doc_books_importance": -161.9097442626953,
"rps_doc_books_importance_length_correction": -158.6744384765625,
"rps_doc_openwebtext_importance": -81.82489013671875,
"rps_doc_openwebtext_importance_length_correction": -81.82489013671875,
"rps_doc_wikipedia_importance": -73.02110290527344,
"rps_doc_wikipedia_importance_length_correction": -65.2323226928711
},
"fasttext": {
"dclm": 0.025621769949793816,
"english": 0.923576831817627,
"fineweb_edu_approx": 1.1600812673568726,
"eai_general_math": 0.009393329732120037,
"eai_open_web_math": 0.09217529743909836,
"eai_web_code": 0.0009708399884402752
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.6",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "-1",
"labels": {
"level_1": "",
"level_2": "",
"level_3": ""
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "21",
"label": "Customer Support"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "2",
"label": "Partially Correct"
}
},
"education_level": {
"primary": {
"code": "1",
"label": "General Audience"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
3,397,268,332,888,510,500
|
Application extensions for Siemens NX with the NXOpen interface
Would you require more information on this topic?
Please request a free consultation appointment with us.
Application extensions for Siemens NX with the NXOpen interface
Siemens NX - small helpers, big Impact -
The use of existing standard systems in the company creates, besides the undisputed advantages of the use of widespread software, a limitation of the own processes to possibilities provided by the software. This does not only apply to office applications, browsers or ERP systems, but also to CAx and PLM software.
The aforementioned restrictions can cause unwanted additional work here, for example through many clicks and extensive methods, or simply prevent desired processes.
The major manufacturers of widely used applications are well aware of this fact and therefore frequently offer programming interfaces for extensions.
Many companies rely on powerful CAx systems for their individual processes in the areas of design, construction and manufacturing. Leading systems such as CATIA V5, SolidEdge or Inventor offer interfaces to extend functionality. Such an interface is also offered and widely used for the Siemens NX CAx application.
The so-called NXOpen interface offers the possibility to create and use custom application extensions for NX in different programming languages.
The interface is based on an object-oriented class structure that provides the user with all required classes and structures with their functions. This class structure is available in the C/C++, Java programming languages and as wrapper, the C/C++ structure also for the .NET languages C# and VB.NET. SWMS uses the modern language variants C# and VB.NET to extend Siemens NX.
Singletons as entry and formal conventions
The easiest way to get started with NXOpen programming is to record and evaluate journals. These can be recorded in the desired language in the corresponding menu and then serve as a template for your own development.
NXOpen Singletons
Figure 1: NXOpen Singletons
Journals follow a fixed scheme, just as their own applications should. For example, this scheme specifies the important function names, which are then used by NX to jump into its own application. The best example of this is the Main function, which in most cases is the main entry. In this function, the first connection points to the current NX session are usually set in recorded journals. The most important connection is the session i.e. the current session. The assignment is done by a relatively seldom used singleton, here the "GetSession". Starting from this session object, all data types, the parts loaded within the session, etc., can be used. The Singleton implementation allows the developer to use this call multiple times in the application because the same object is always returned.
Limits of Object Orientation for Recorded Journals
Recorded journals are an important starting point for your own development. They are used to gain an insight into the processes within Siemens NX and to record the appropriate use of the available objects and functions. However, this valuable tool also has its limitations. This is especially true in the area of user interaction. If a function is recorded in which the user has to make a manual entry - in our example the edge length of a cuboid - this is only recorded transparently in the recorded code. In the example shown below, in the case of edge lengths, you can see the numerical values entered ("100") without knowing their origin. Such and similar cases naturally present a small challenge on the way from the recorded journal to your own application. Cleverly substituted by custom input possibilities and can however quickly be further developed from such a journal.
NXOpen Journal
Figure 2: NXOpen Journal
The output of simple information, such as the number of components in the assembly, article lists, weights, dimensions and many others, is also a very popular and widespread application. The import and export of geometries and metadata also plays an important role in the development of NXOpen extensions.
Many of these capabilities can even be automated without a costly additional license.
By using journals one loses some comfort in the development, but also saves license costs compared to fully trained applications, which have to be signed with a special license.
Based on basic examples such as the one shown above, it is possible to develop applications of any complexity and use them in everyday product design. This includes the possibility to use individually designed user interfaces with the help of common frameworks (Forms, WPF, etc.) or to compile an NX-custom interface from prefabricated components in the so-called Blockstyler, an additional application in Siemens NX.
Example of user interface with Blockstyler
Figure 3: Magic NX Wizzard
Development opportunities with NXOpen
The NXOpen interface between the NX CAx platform and a self-created application offers various possibilities for the automation of the entire system. This opens up opportunities to simplify your own work. A typical example here is to automate frequently performed use cases, such as the export to an exchange format, so that instead of several clicks in the corresponding NX wizard, the export with the desired settings takes place with one click.
Conclusion
Even if many don't believe it at first: Such small aids save a lot of time and spare the nerves of the user.
They also provide a good introduction to an individually adapted environment. Design assistants, intelligent component adaptations and specific tests are further options for using the system more efficiently and reducing time-consuming routine work. Finding a way to work is initially difficult for some, but once a good basic framework has been created, the continuation of the work becomes increasingly easier. Small little helpers that are easy to implement and also convince some superiors to allocate time and capacities for corresponding activities.
Noch keine Kommentare vorhanden.
Was denkst du?
Popular Posts
Locations
Oldenburg
SWMS Systemtechnik Ingenieurgesellschaft mbH
Donnerschweer Straße 4a, 26123 Oldenburg
info@swms.de
+49 (0) 441 960 21 0
SWMS Consulting GmbH
Donnerschweer Straße 4a, 26123 Oldenburg consulting@swms.de
+49 (0) 441 559 795 25
Bremen
SWMS Technologies GmbH
World Trade Center
Hermann-Köhl Str. 7, 28199 Bremen technologies@swms.de
+49 (0) 421 960 12 30
Copyright © 1996 SWMS Systemtechnik Ingenieurgesellschaft mbH. | Impressum, Datenschutz, AGBs
|
{
"url": "https://www.swms.de/en/blog/application-extensions-for-siemens-nx-with-the-nxopen-interface/",
"source_domain": "www.swms.de",
"snapshot_id": "crawl=CC-MAIN-2019-26",
"warc_metadata": {
"Content-Length": "32652",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:UN3KW2JCIYIPSU7JSLKH5VFR5KHX5JPK",
"WARC-Concurrent-To": "<urn:uuid:adf37533-53cd-4935-ba47-940419382779>",
"WARC-Date": "2019-06-16T17:23:12Z",
"WARC-IP-Address": "178.63.79.73",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:YKN2Y42YCPN5I7RT7CFLNQBGKNXHQ7SG",
"WARC-Record-ID": "<urn:uuid:0fe75303-8b27-46a9-b3e6-6216b956d6db>",
"WARC-Target-URI": "https://www.swms.de/en/blog/application-extensions-for-siemens-nx-with-the-nxopen-interface/",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:bc1ef8b6-1ccd-4f28-a44a-4eb4f26ab2e3>"
},
"warc_info": "isPartOf: CC-MAIN-2019-26\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for June 2019\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-187-26-184.ec2.internal\r\nsoftware: Apache Nutch 1.15 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.1-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
64,
65,
115,
116,
172,
173,
237,
238,
279,
280,
595,
596,
761,
762,
912,
913,
1228,
1229,
1374,
1375,
1751,
1752,
1795,
1796,
2014,
2015,
2033,
2034,
2062,
2063,
2863,
2864,
2915,
2916,
3797,
3798,
3813,
3814,
3839,
3840,
4146,
4147,
4233,
4234,
4412,
4413,
4831,
4832,
4875,
4876,
4903,
4904,
4942,
4943,
5391,
5392,
5403,
5404,
5513,
5514,
6070,
6071,
6104,
6105,
6120,
6121,
6135,
6136,
6146,
6147,
6157,
6202,
6243,
6256,
6277,
6298,
6358,
6381,
6388,
6411,
6430,
6485,
6507
],
"line_end_idx": [
64,
65,
115,
116,
172,
173,
237,
238,
279,
280,
595,
596,
761,
762,
912,
913,
1228,
1229,
1374,
1375,
1751,
1752,
1795,
1796,
2014,
2015,
2033,
2034,
2062,
2063,
2863,
2864,
2915,
2916,
3797,
3798,
3813,
3814,
3839,
3840,
4146,
4147,
4233,
4234,
4412,
4413,
4831,
4832,
4875,
4876,
4903,
4904,
4942,
4943,
5391,
5392,
5403,
5404,
5513,
5514,
6070,
6071,
6104,
6105,
6120,
6121,
6135,
6136,
6146,
6147,
6157,
6202,
6243,
6256,
6277,
6298,
6358,
6381,
6388,
6411,
6430,
6485,
6507,
6600
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 6600,
"ccnet_original_nlines": 83,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3855932056903839,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.03050846979022026,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.14406779408454895,
"rps_doc_frac_unique_words": 0.43768399953842163,
"rps_doc_mean_word_length": 5.292443752288818,
"rps_doc_num_sentences": 60,
"rps_doc_symbol_to_word_ratio": 0.0016949200071394444,
"rps_doc_unigram_entropy": 5.441318988800049,
"rps_doc_word_count": 1019,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.033376600593328476,
"rps_doc_frac_chars_dupe_6grams": 0.02039681002497673,
"rps_doc_frac_chars_dupe_7grams": 0.02039681002497673,
"rps_doc_frac_chars_dupe_8grams": 0.02039681002497673,
"rps_doc_frac_chars_dupe_9grams": 0.02039681002497673,
"rps_doc_frac_chars_top_2gram": 0.013906920328736305,
"rps_doc_frac_chars_top_3gram": 0.013350640423595905,
"rps_doc_frac_chars_top_4gram": 0.011496379971504211,
"rps_doc_books_importance": -557.7411499023438,
"rps_doc_books_importance_length_correction": -557.7411499023438,
"rps_doc_openwebtext_importance": -303.83758544921875,
"rps_doc_openwebtext_importance_length_correction": -303.83758544921875,
"rps_doc_wikipedia_importance": -237.7879638671875,
"rps_doc_wikipedia_importance_length_correction": -237.7879638671875
},
"fasttext": {
"dclm": 0.020519079640507698,
"english": 0.9103466272354126,
"fineweb_edu_approx": 2.6605539321899414,
"eai_general_math": 0.7544603943824768,
"eai_open_web_math": 0.18582743406295776,
"eai_web_code": 0.3714466094970703
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.4",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "621.00113",
"labels": {
"level_1": "Industrial arts, Technology, and Engineering",
"level_2": "Engineering",
"level_3": "Mechanical engineering and Machinery"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "4",
"label": "Missing Images or Figures"
},
"secondary": {
"code": "0",
"label": "No missing content"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "10",
"label": "Knowledge Article"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-613,725,151,103,483,300
|
利用 iframe 实现网页嵌套的方法,实现站中站网页
如果你有个域名和服务器,但是你又想要目标网站的内容,可以选择套壳,用html的iframe标签实现。
代码如下
<!DOCTYPE html>
<html lang="zh">
<head>
<meta charset="UTF-8">
<meta http-equiv="X-UA-Compatible" content="IE=edge">
<meta http-equiv="Content-Security-Policy" content="upgrade-insecure-requests">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<link rel="stylesheet" href="main.css">
<title>大海资源库地址发布页:dahkk.cn 关注微信公众号:大海资源库 </title>
<meta name="keywords" content="大海资源库" />
<meta name="description" content="大海资源库">
<link rel="shortcut icon" href="http://www.xgw5.com/favicon.ico" type="image/x-icon">
<style>
body {
margin: 0;
padding: 0;
}
#myiframe {
width: 100%;
height: 100vh;
border: none;
}
</style>
<script>
function changeFrameHeight() {
var ifm = document.getElementById("myiframe");
ifm.height = document.documentElement.clientHeight;
}
window.onresize = function() {
changeFrameHeight();
};
</script>
</head>
<body>
<iframe src="https://www.xgw5.com" id="myiframe" scrolling="yes" onload="changeFrameHeight()" frameborder="0"></iframe>
</body>
</html>
说明一下
以上代码实现,自动适配屏幕缩放。
无边框,带滚动
自动适配目标网址的SSL.
再最下方的 iframe src= 后方替换自己的目标网址即可
有问题及时联系站长,QQ:1240555208
更多优质资源在QQ群里,可以进群领取:467392290~
© 版权声明
THE END
点赞14
及时反馈~ 抢沙发
请登录后发表评论
暂无评论内容
|
{
"url": "https://dahkk.cn/4254.html",
"source_domain": "dahkk.cn",
"snapshot_id": "CC-MAIN-2024-30",
"warc_metadata": {
"Content-Length": "135785",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:B3OHKY74F3PKTDMUH4AQVO4NT6C44HJ5",
"WARC-Concurrent-To": "<urn:uuid:2a81a610-4889-450c-b3bb-b6eb1036b3d8>",
"WARC-Date": "2024-07-18T03:53:25Z",
"WARC-IP-Address": "154.12.27.82",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:LE4AGMIUZEO32XXLD52E45C55JAZXOYR",
"WARC-Record-ID": "<urn:uuid:82185785-77d7-4c2a-8d56-eb540902d395>",
"WARC-Target-URI": "https://dahkk.cn/4254.html",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:7b2a84a8-c58d-4580-ae50-2dd3abdff65a>"
},
"warc_info": "isPartOf: CC-MAIN-2024-30\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for July 2024\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-28\r\nsoftware: Apache Nutch 1.20 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.5-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
28,
29,
80,
81,
86,
87,
88,
104,
121,
128,
130,
132,
157,
213,
216,
296,
299,
372,
414,
416,
470,
513,
557,
560,
648,
651,
653,
656,
666,
677,
694,
712,
718,
734,
753,
774,
794,
800,
811,
822,
857,
910,
968,
974,
1009,
1036,
1043,
1055,
1063,
1070,
1192,
1200,
1208,
1209,
1214,
1215,
1232,
1233,
1241,
1242,
1256,
1257,
1289,
1290,
1314,
1344,
1351,
1359,
1364,
1374,
1375,
1384,
1385
],
"line_end_idx": [
28,
29,
80,
81,
86,
87,
88,
104,
121,
128,
130,
132,
157,
213,
216,
296,
299,
372,
414,
416,
470,
513,
557,
560,
648,
651,
653,
656,
666,
677,
694,
712,
718,
734,
753,
774,
794,
800,
811,
822,
857,
910,
968,
974,
1009,
1036,
1043,
1055,
1063,
1070,
1192,
1200,
1208,
1209,
1214,
1215,
1232,
1233,
1241,
1242,
1256,
1257,
1289,
1290,
1314,
1344,
1351,
1359,
1364,
1374,
1375,
1384,
1385,
1395
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 1395,
"ccnet_original_nlines": 73,
"rps_doc_curly_bracket": 0.005734770093113184,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.024844719097018242,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.03105589933693409,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.6086956262588501,
"rps_doc_frac_unique_words": 0.7978723645210266,
"rps_doc_mean_word_length": 10.021276473999023,
"rps_doc_num_sentences": 16,
"rps_doc_symbol_to_word_ratio": 0.0031055898871272802,
"rps_doc_unigram_entropy": 4.205758571624756,
"rps_doc_word_count": 94,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.053078558295965195,
"rps_doc_frac_chars_top_3gram": 0,
"rps_doc_frac_chars_top_4gram": 0,
"rps_doc_books_importance": -130.7693328857422,
"rps_doc_books_importance_length_correction": -130.72804260253906,
"rps_doc_openwebtext_importance": -73.99649047851562,
"rps_doc_openwebtext_importance_length_correction": -73.99649047851562,
"rps_doc_wikipedia_importance": -26.48058319091797,
"rps_doc_wikipedia_importance_length_correction": -23.63964080810547
},
"fasttext": {
"dclm": 0.9996479749679565,
"english": 0.09170881658792496,
"fineweb_edu_approx": 3.040419340133667,
"eai_general_math": 0.01763940043747425,
"eai_open_web_math": 0.0003576299932319671,
"eai_web_code": 0.8676273226737976
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.678",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "23",
"label": "Tutorial"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
4,478,615,964,823,829,000
|
View Javadoc
1 /*
2 wsmo4j - a WSMO API and Reference Implementation
3 Copyright (c) 2005, University of Innsbruck, Austria
4 This library is free software; you can redistribute it and/or modify it under
5 the terms of the GNU Lesser General Public License as published by the Free
6 Software Foundation; either version 2.1 of the License, or (at your option)
7 any later version.
8 This library is distributed in the hope that it will be useful, but WITHOUT
9 ANY WARRANTY; without even the implied warranty of MERCHANTABILITY or FITNESS
10 FOR A PARTICULAR PURPOSE. See the GNU Lesser General Public License for more
11 details.
12 You should have received a copy of the GNU Lesser General Public License along
13 with this library; if not, write to the Free Software Foundation, Inc.,
14 59 Temple Place, Suite 330, Boston, MA 02111-1307 USA
15 */
16 package org.deri.wsmo4j.validator;
17
18 import java.util.HashMap;
19 import java.util.HashSet;
20 import java.util.Iterator;
21 import java.util.List;
22 import java.util.Map;
23 import java.util.Set;
24 import java.util.Vector;
25
26 import org.deri.wsmo4j.io.serializer.wsml.LogExprSerializerWSML;
27 import org.deri.wsmo4j.logicalexpression.ConstantTransformer;
28 import org.omwg.logicalexpression.Atom;
29 import org.omwg.logicalexpression.AtomicExpression;
30 import org.omwg.logicalexpression.AttributeConstraintMolecule;
31 import org.omwg.logicalexpression.AttributeInferenceMolecule;
32 import org.omwg.logicalexpression.AttributeValueMolecule;
33 import org.omwg.logicalexpression.Binary;
34 import org.omwg.logicalexpression.CompoundMolecule;
35 import org.omwg.logicalexpression.Conjunction;
36 import org.omwg.logicalexpression.Constraint;
37 import org.omwg.logicalexpression.Disjunction;
38 import org.omwg.logicalexpression.Equivalence;
39 import org.omwg.logicalexpression.ExistentialQuantification;
40 import org.omwg.logicalexpression.Implication;
41 import org.omwg.logicalexpression.InverseImplication;
42 import org.omwg.logicalexpression.LogicProgrammingRule;
43 import org.omwg.logicalexpression.LogicalExpression;
44 import org.omwg.logicalexpression.MembershipMolecule;
45 import org.omwg.logicalexpression.Molecule;
46 import org.omwg.logicalexpression.Negation;
47 import org.omwg.logicalexpression.NegationAsFailure;
48 import org.omwg.logicalexpression.SubConceptMolecule;
49 import org.omwg.logicalexpression.UniversalQuantification;
50 import org.omwg.logicalexpression.Visitor;
51 import org.omwg.logicalexpression.terms.Term;
52 import org.omwg.ontology.Axiom;
53 import org.omwg.ontology.Variable;
54 import org.wsmo.common.WSML;
55 import org.wsmo.factory.LogicalExpressionFactory;
56 import org.wsmo.validator.ValidationError;
57
58
59 /**
60 * Checks logical expressions for wsml-core validity.
61 *
62 * <pre>
63 * Created on Aug 19, 2005
64 * Committed by $Author: morcen $
65 * $Source$,
66 * </pre>
67 *
68 * @author nathalie.steinmetz@deri.org
69 * @version $Revision: 1946 $ $Date: 2007-04-02 15:13:28 +0300 (Mon, 02 Apr 2007) $
70 */
71 public class WsmlCoreExpressionValidator
72 implements Visitor{
73
74 private Set <Term> equivVariables = null;
75
76 private Set <Term> lhsVariables = null;
77
78 private Set <Term> rhsVariables = null;
79
80 private int numberOfMolecules = 0;
81
82 private Set <List <Term>> molecules = null;
83
84 private WsmlCoreValidator validator = null;
85
86 private LogExprSerializerWSML leSerializer = null;
87
88 private LogicalExpressionFactory leFactory = null;
89
90 private Axiom axiom = null;
91
92 private List <ValidationError> errors = null;
93
94 private String error;
95
96 private boolean formula;
97
98 private boolean rhs;
99
100 private boolean lhs;
101
102 private boolean errorFlag;
103
104
105 /**
106 * @param axiom whose logical expression is checked
107 * @param errors list that will be filled with error messages of found variant violations
108 */
109 protected WsmlCoreExpressionValidator(Axiom axiom, LogicalExpressionFactory leFactory, List <ValidationError> errors, WsmlCoreValidator val) {
110 this.axiom = axiom;
111 this.errors = errors;
112 this.validator = val;
113 leSerializer = validator.leSerializer;
114 this.leFactory = leFactory;
115 }
116
117 protected void setup() {
118 lhsVariables = new HashSet <Term> ();
119 numberOfMolecules = 0;
120 molecules = new HashSet <List <Term>> ();
121 equivVariables = new HashSet <Term> ();
122 lhsVariables = new HashSet <Term> ();
123 rhsVariables = new HashSet <Term> ();
124 formula = false;
125 rhs = false;
126 lhs = false;
127 errorFlag = true;
128 }
129
130 /**
131 * Checks if an atom is valid to wsml-core.
132 *
133 * @see org.deri.wsmo4j.validator.WsmlFlightExpressionValidator#visitAtom(org.omwg.logicalexpression.Atom)
134 */
135 public void visitAtom(Atom expr) {
136 Molecule molecule = atomToMolecule(expr);
137 if (molecule != null) {
138 molecule.accept(this);
139 }
140 }
141
142 /**
143 * Checks if an AttributeConstraintMolecule is valid to wsml-core.
144 *
145 * @see org.deri.wsmo4j.validator.WsmlFlightExpressionValidator#visitAttributeContraintMolecule(org.omwg.logicalexpression.AttributeConstraintMolecule)
146 */
147 public void visitAttributeContraintMolecule(AttributeConstraintMolecule expr) {
148 String error = ":\n Cannot contain an AttributeConstraintMolecule:\n"
149 + leSerializer.serialize(expr);
150 // An AttributeConstraintMolecule is no valid right-hand side formula
151 if (rhs) {
152 if (errorFlag) {
153 addError(expr, ValidationError.AX_RHS_ERR + error);
154 }
155 }
156 else if (lhs) {
157 if (errorFlag) {
158 addError(expr, ValidationError.AX_LHS_ERR + error);
159 }
160 }
161 else {
162 // the identifier must be a Concept
163 if (check(expr.getLeftParameter(), false, true, true, true, true)) {
164 addError(expr, ValidationError.AX_ATOMIC_ERR + ":"
165 + "\nThe range identifier must be a Concept, " +
166 "not a " + error + "\n" + leSerializer.serialize(expr));
167 }
168 // the arguments must be datatypes
169 if (check(expr.getRightParameter(), true, true, true, false, true)) {
170 addError(expr, ValidationError.AX_ATOMIC_ERR + ":"
171 + "\nThe arguments must be " +
172 "Datatypes, not " + error + "\n" + leSerializer.serialize(expr));
173 }
174 // the attribute's name must be a Relation with concrete range
175 if ((check(expr.getAttribute(), true, true, false, true, true))
176 || (!checkConcreteRelations(expr.getAttribute()))){
177 addError(expr, ValidationError.AX_ATOMIC_ERR + ":"
178 + "\nThe name must be a Relation with concrete range, " +
179 "not a " + error + "\n" + leSerializer.serialize(expr));
180 }
181 }
182 }
183
184 /**
185 * Checks if an AttributeInferenceMolecule is valid to wsml-core.
186 *
187 * @see org.deri.wsmo4j.validator.WsmlFlightExpressionValidator#visitAttributeInferenceMolecule(org.omwg.logicalexpression.AttributeInferenceMolecule)
188 */
189 public void visitAttributeInferenceMolecule(AttributeInferenceMolecule expr) {
190 String error = ":\n Cannot contain an AttributeInferenceMolecule:\n"
191 + leSerializer.serialize(expr);
192 // An AttributeInferenceMolecule is no valid right-hand side formula
193 if (rhs) {
194 if (errorFlag) {
195 addError(expr, ValidationError.AX_RHS_ERR + error);
196 }
197 }
198 else if (lhs) {
199 if (errorFlag) {
200 addError(expr, ValidationError.AX_LHS_ERR + error);
201 }
202 }
203 else {
204 // the identifier must be a Concept
205 if (check(expr.getLeftParameter(), false, true, true, true, true)) {
206 addError(expr, ValidationError.AX_ATOMIC_ERR + ":"
207 + "\nThe range identifier must be a Concept, " +
208 "not a " + error + "\n" + leSerializer.serialize(expr));
209 }
210 // the arguments of an infering attribute must be datatypes or concepts
211 if (check(expr.getRightParameter(), false, true, true, false, true)) {
212 addError(expr, ValidationError.AX_ATOMIC_ERR + ": \nThe arguments " +
213 "must be Datatypes or Concepts, " +
214 "not " + error + "\n" + leSerializer.serialize(expr));
215 }
216 else {
217 // if the argument is a datatype, the attribute's name must be a relation with concrete range
218 if (checkDatatypes(expr.getRightParameter())) {
219 if (!checkConcreteRelations(expr.getAttribute())) {
220 addError(expr, ValidationError.AX_ATOMIC_ERR + ": \nThe name " +
221 "must be a relation with concrete range " +
222 "(because the argument is a datatype)\n" + leSerializer.serialize(expr));
223 }
224 }
225 // if the argument is a concept, the attribute's name must be a relation with abstract range
226 else if (checkConcepts(expr.getRightParameter())) {
227 if (!checkAbstractRelations(expr.getAttribute())) {
228 addError(expr, ValidationError.AX_ATOMIC_ERR + ": \nThe name " +
229 "must be a relation with abstract range " +
230 "(because the argument is a concept)\n" + leSerializer.serialize(expr));
231 }
232 }
233 }
234 }
235 }
236
237 /**
238 * Checks if an AttributeValueMolecule is valid to wsml-core.
239 *
240 * @see org.deri.wsmo4j.validator.WsmlFlightExpressionValidator#visitAttributeValueMolecule(org.omwg.logicalexpression.AttributeValueMolecule)
241 */
242 public void visitAttributeValueMolecule(AttributeValueMolecule expr) {
243 // An AttributeValueMolecule is no valid right-hand side formula
244 if (rhs) {
245 if (errorFlag) {
246 addError(expr, ValidationError.AX_RHS_ERR + ":\n Cannot " +
247 "contain an AttributeValueMolecule:\n"
248 + leSerializer.serialize(expr));
249 }
250 }
251 // check if an AttributeValueMolecule is a valid b-molecule
252 if (lhs || formula) {
253 // the identifier of the molecule must be a variable
254 if (!(expr.getLeftParameter() instanceof Variable)) {
255 if (errorFlag) {
256 addError(expr, ValidationError.AX_FORMULA_ERR + ": A valid b-molecule " +
257 "must contain a variable as identifier\n" + leSerializer.serialize(expr));
258 }
259 return;
260 }
261 else if (!lhsVariables.contains(expr.getLeftParameter())) {
262 lhsVariables.add(expr.getLeftParameter());
263 }
264
265 // the name of the attribute must be a relation
266 if (!checkAbstractRelations(expr.getAttribute())) {
267 if (errorFlag) {
268 addError(expr, ValidationError.AX_FORMULA_ERR + ": A valid b-molecule's " +
269 "attribute name must be a relation with abstract range\n"
270 + leSerializer.serialize(expr));
271 }
272 return;
273 }
274
275 // the arguments of the attribute must be variables
276 if (!(expr.getRightParameter() instanceof Variable)) {
277 if (errorFlag) {
278 addError(expr, ValidationError.AX_FORMULA_ERR + ": A valid b-molecule's " +
279 "attribute's arguments must be variables\n" + leSerializer.serialize(expr));
280 }
281 return;
282 }
283 else if (!lhsVariables.contains(expr.getRightParameter())) {
284 lhsVariables.add(expr.getRightParameter());
285 }
286
287 List <Term> l = new Vector <Term> ();
288 l.add(expr.getLeftParameter());
289 if (!expr.getLeftParameter().equals(expr.getRightParameter())) {
290 l.add(expr.getRightParameter());
291 }
292 numberOfMolecules = numberOfMolecules + 1;
293 molecules.add(l);
294 }
295 else {
296 // the identifier must be an Instance
297 if (check(expr.getLeftParameter(), true, false, true, true, true)) {
298 addError(expr, ValidationError.AX_ATOMIC_ERR + ":"
299 + "\nThe range identifier must be an Instance, " +
300 "not a " + error + "\n" + leSerializer.serialize(expr));
301 }
302 // the arguments of a value definition attribute must be DataValues or Instances
303 if (check(expr.getRightParameter(), true, false, true, false, true)) {
304 addError(expr, ValidationError.AX_ATOMIC_ERR + ":\nThe arguments " +
305 "must be DataValues or Instances, " +
306 "not " + error + "\n" + leSerializer.serialize(expr));
307 }
308 else {
309 // if the argument is a DataValue, the attribute's name must be a relation with concrete range
310 if (checkDatatypes(expr.getRightParameter())) {
311 if (!checkConcreteRelations(expr.getAttribute())) {
312 addError(expr, ValidationError.AX_ATOMIC_ERR + ": \nThe name " +
313 "must be a relation with concrete range " +
314 "(because the argument is a DataValue)\n" + leSerializer.serialize(expr));
315 }
316 }
317 // if the argument is an instance, the attribute's name must be a relation with abstract range
318 else if (checkInstances(expr.getRightParameter())) {
319 if (!checkAbstractRelations(expr.getAttribute())) {
320 addError(expr, ValidationError.AX_ATOMIC_ERR + ": \nThe name " +
321 "must be a relation with abstract range " +
322 "(because the argument is an instance)\n" + leSerializer.serialize(expr));
323 }
324 }
325 }
326 }
327 }
328
329 /**
330 * Checks if a CompoundMolecule is valid to wsml-core.
331 *
332 * @see org.deri.wsmo4j.validator.WsmlFlightExpressionValidator#visitCompoundMolecule(org.omwg.logicalexpression.CompoundMolecule)
333 */
334 public void visitCompoundMolecule(CompoundMolecule expr) {
335 Iterator i = expr.listOperands().iterator();
336 while(i.hasNext()){
337 ((Molecule)i.next()).accept(this);
338 }
339 }
340
341 /**
342 * Checks if a MembershipMolecule is valid to wsml-core.
343 *
344 * @see org.deri.wsmo4j.validator.WsmlFlightExpressionValidator#visitMemberShipMolecule(org.omwg.logicalexpression.MembershipMolecule)
345 */
346 public void visitMemberShipMolecule(MembershipMolecule expr) {
347 // Checks if a MembershipMolecule is a valid a-molecule
348 if (rhs) {
349 // the identifier of the molecule must be a variable
350 if (!(expr.getLeftParameter() instanceof Variable)) {
351 if (errorFlag) {
352 addError(expr, ValidationError.AX_FORMULA_ERR + ":\n A valid a-molecule " +
353 "must contain a variable as identifier\n" + leSerializer.serialize(expr));
354 }
355 }
356 else {
357 if (!equivVariables.contains(expr.getLeftParameter())) {
358 equivVariables.add(expr.getLeftParameter());
359 }
360 if (!rhsVariables.contains(expr.getLeftParameter())) {
361 rhsVariables.add(expr.getLeftParameter());
362 }
363 }
364 // the argument of the molecule must be a Concept
365 if (check(expr.getRightParameter(), false, true, true, true, true)) {
366 if (errorFlag) {
367 addError(expr, ValidationError.AX_FORMULA_ERR + ":"
368 + "\nError: The arguments of an a-molecule must be Concepts\n"
369 + leSerializer.serialize(expr));
370 }
371 }
372 }
373 else if (lhs) {
374 if (errorFlag) {
375 addError(expr, ValidationError.AX_LHS_ERR + ":\n Cannot " +
376 "contain a MembershipMolecule:\n"
377 + leSerializer.serialize(expr));
378 }
379 }
380 else {
381 // the identifier must be an Instance
382 if (check(expr.getLeftParameter(), true, false, true, true, true)) {
383 addError(expr, ValidationError.AX_ATOMIC_ERR + ":"
384 + "\nThe identifier must be an Instance, " +
385 "not a " + error + "\n" + leSerializer.serialize(expr));
386 }
387 // the arguments must be Concepts
388 if (check(expr.getRightParameter(), false, true, true, true, true)) {
389 addError(expr, ValidationError.AX_ATOMIC_ERR + ":"
390 + "\nThe arguments must be Concepts, " +
391 "not " + error + "\n" + leSerializer.serialize(expr));
392 }
393 }
394 }
395
396 /**
397 * Checks if a SubConceptMolecule is valid to wsml-core.
398 *
399 * @see org.deri.wsmo4j.validator.WsmlFlightExpressionValidator#visitSubConceptMolecule(org.omwg.logicalexpression.SubConceptMolecule)
400 */
401 public void visitSubConceptMolecule(SubConceptMolecule expr) {
402 String error = ":\n Cannot contain a SubConceptMolecule:\n"
403 + leSerializer.serialize(expr);
404 // A SubConceptMolecule is no valid right-hand side formula
405 if (rhs) {
406 if (errorFlag) {
407 addError(expr, ValidationError.AX_RHS_ERR + error);
408 }
409 }
410 else if (lhs) {
411 if (errorFlag) {
412 addError(expr, ValidationError.AX_LHS_ERR + error);
413 }
414 }
415 else {
416 error = "";
417 // the identifier must be a Concept
418 if (check(expr.getLeftParameter(), false, true, true, true, true)) {
419 addError(expr, ValidationError.AX_ATOMIC_ERR + ":"
420 + "\nThe identifier must be a Concept, " +
421 "not a " + error + "\n" + leSerializer.serialize(expr));
422 }
423 // the arguments must be Concepts
424 if (check(expr.getRightParameter(), false, true, true, true, true)) {
425 addError(expr, ValidationError.AX_ATOMIC_ERR + ":"
426 + "\nThe arguments must be Concepts, " +
427 "not " + error + "\n" + leSerializer.serialize(expr));
428 }
429 }
430 }
431
432 /**
433 * Checks if a Negation is valid to wsml-core.
434 *
435 * @see org.deri.wsmo4j.validator.WsmlFlightExpressionValidator#visitNegation(org.omwg.logicalexpression.Negation)
436 */
437 public void visitNegation(Negation expr) {
438 String error = ":\n Cannot contain a Negation:\n"
439 + leSerializer.serialize(expr);
440 // A negation is no valid right-hand side formula
441 if (rhs) {
442 if (errorFlag) {
443 addError(expr, ValidationError.AX_RHS_ERR + error);
444 }
445 }
446 else if (lhs) {
447 if (errorFlag) {
448 addError(expr, ValidationError.AX_LHS_ERR + error);
449 }
450 }
451 else {
452 addError(expr, ValidationError.AX_FORMULA_ERR + ": A Negation is" +
453 " not a valid formula\n" + leSerializer.serialize(expr));
454 }
455 }
456
457 /**
458 * Checks if a NegationAsFailure is valid to wsml-core.
459 *
460 * @see org.deri.wsmo4j.validator.WsmlFlightExpressionValidator#visitNegationAsFailure(org.omwg.logicalexpression.NegationAsFailure)
461 */
462 public void visitNegationAsFailure(NegationAsFailure expr) {
463 String error = ":\n Cannot contain a NegationAsFailure:\n"
464 + leSerializer.serialize(expr);
465 // A NegationAsFailure is no valid right-hand side formula
466 if (rhs) {
467 if (errorFlag) {
468 addError(expr, ValidationError.AX_RHS_ERR + error);
469 }
470 }
471 else if (lhs) {
472 if (errorFlag) {
473 addError(expr, ValidationError.AX_LHS_ERR + error);
474 }
475 }
476 else {
477 addError(expr, ValidationError.AX_FORMULA_ERR + ": A NegationAsFailure " +
478 "is not a valid formula\n" + leSerializer.serialize(expr));
479 }
480 }
481
482 /**
483 * Checks if a Constraint is valid to wsml-core.
484 *
485 * @see org.deri.wsmo4j.validator.WsmlFlightExpressionValidator#visitConstraint(org.omwg.logicalexpression.Constraint)
486 */
487 public void visitConstraint(Constraint expr) {
488 String error = ":\n Cannot contain a Constraint:\n"
489 + leSerializer.serialize(expr);
490 // A Constraint is no valid right-hand side formula
491 if (rhs) {
492 if (errorFlag) {
493 addError(expr, ValidationError.AX_RHS_ERR + error);
494 }
495 }
496 else if (lhs) {
497 if (errorFlag) {
498 addError(expr, ValidationError.AX_LHS_ERR + error);
499 }
500 }
501 else {
502 addError(expr, ValidationError.AX_FORMULA_ERR + ": A Constraint is not " +
503 "a valid formula\n" + leSerializer.serialize(expr));
504 }
505 }
506
507 /**
508 * Checks if a Conjunction is valid to wsml-core.
509 *
510 * @see org.deri.wsmo4j.validator.WsmlFlightExpressionValidator#visitConjunction(org.omwg.logicalexpression.Conjunction)
511 */
512 public void visitConjunction(Conjunction expr) {
513 // Checks if a Conjunction is a valid right-hand side formula
514 if (rhs || lhs) {
515 expr.getLeftOperand().accept(this);
516 expr.getRightOperand().accept(this);
517 }
518 else {
519 if((expr.getLeftOperand() instanceof Conjunction)
520 || (expr.getLeftOperand() instanceof AtomicExpression)){
521 expr.getLeftOperand().accept(this);
522 }
523 else {
524 addError(expr, ValidationError.AX_FORMULA_ERR + ": Invalid " +
525 "Conjunction, all operands must be valid atomic " +
526 "formulae\n" + leSerializer.serialize(expr));
527 }
528 if ((expr.getRightOperand() instanceof Conjunction)
529 || (expr.getRightOperand() instanceof AtomicExpression)){
530 expr.getRightOperand().accept(this);
531 }
532 else {
533 addError(expr, ValidationError.AX_FORMULA_ERR + ": Invalid " +
534 "Conjunction, all operands must be valid atomic " +
535 "formulae\n" + leSerializer.serialize(expr));
536 }
537 }
538 }
539
540 /**
541 * Checks if a Disjunction is valid to wsml-core.
542 *
543 * @see org.deri.wsmo4j.validator.WsmlFlightExpressionValidator#visitDisjunction(org.omwg.logicalexpression.Disjunction)
544 */
545 public void visitDisjunction(Disjunction expr) {
546 // A Disjunction is no valid right-hand side formula
547 if (rhs) {
548 if (errorFlag) {
549 addError(expr, ValidationError.AX_RHS_ERR + ":\n Cannot " +
550 "contain a Disjunction:\n" + leSerializer.serialize(expr));
551 }
552 }
553 // Checks if a specified Disjunction is a valid left-hand side formula
554 else if (lhs) {
555 expr.getLeftOperand().accept(this);
556 expr.getRightOperand().accept(this);
557 }
558 else {
559 addError(expr, ValidationError.AX_FORMULA_ERR + ": A Disjunction is not " +
560 "a valid formula\n" + leSerializer.serialize(expr));
561 }
562 }
563
564 /**
565 * Checks if an InverseImplication is valid to wsml-core.
566 *
567 * @see org.deri.wsmo4j.validator.WsmlFlightExpressionValidator#visitInverseImplication(org.omwg.logicalexpression.InverseImplication)
568 */
569 public void visitInverseImplication(InverseImplication expr) {
570 String error = ":\n Cannot contain an InverseImplication:\n"
571 + leSerializer.serialize(expr);
572 // An InverseImplication is no valid right-hand side formula
573 if (rhs) {
574 if (errorFlag) {
575 addError(expr, ValidationError.AX_RHS_ERR + error);
576 }
577 }
578 else if (lhs) {
579 if (errorFlag) {
580 addError(expr, ValidationError.AX_LHS_ERR + error);
581 }
582 }
583 else {
584 rhsVariables.clear();
585 lhsVariables.clear();
586 molecules.clear();
587 LogicalExpression left = expr.getLeftOperand();
588 LogicalExpression right = expr.getRightOperand();
589
590 // check on transitive attribute structure
591 if (((left instanceof Atom)
592 || (left instanceof AttributeValueMolecule)) &&
593 (right instanceof Conjunction)) {
594 LogicalExpression leftConjunction = ((Conjunction) right).getLeftOperand();
595 LogicalExpression rightConjunction = ((Conjunction) right).getRightOperand();
596 if (((leftConjunction instanceof Atom)
597 || (leftConjunction instanceof AttributeValueMolecule))
598 && ((rightConjunction instanceof Atom)
599 || (rightConjunction instanceof AttributeValueMolecule))) {
600 isValidTransitiveInvImpl(expr);
601 }
602 }
603 // check on symmetric, sub-attribute and inverse attribute structure
604 else if (((left instanceof Atom) || (left instanceof AttributeValueMolecule)) &&
605 ((right instanceof Atom) || (right instanceof AttributeValueMolecule))) {
606 isValidInverseImplication(expr);
607 }
608 else {
609 // check on right-hand side impliedBy left-hand side structure
610 errorFlag = false;
611 rhs = true;
612 left.accept(this);
613 rhs = false;
614 lhs = true;
615 right.accept(this);
616 lhs = false;
617
618 Iterator it = rhsVariables.iterator();
619 while (it.hasNext()) {
620 if (!lhsVariables.contains(it.next())) {
621 addError(expr, ValidationError.AX_IMPL_BY_ERR + ": All " +
622 "variables in 'a' from 'a impliedBy b' " +
623 "must also be contained in 'b'\n" + leSerializer.serialize(expr));
624 }
625 }
626 if (lhsVariables.size() > 0) {
627 Graph graph = new Graph();
628 graph.isValidGraph(expr);
629 }
630 }
631 }
632 }
633
634 /**
635 * Checks if an Implication is valid to wsml-core.
636 *
637 * @see org.deri.wsmo4j.validator.WsmlFlightExpressionValidator#visitImplication(org.omwg.logicalexpression.Implication)
638 */
639 public void visitImplication(Implication expr) {
640 String error = ":\n Cannot contain an Implication:\n"
641 + leSerializer.serialize(expr);
642 // An Implication is no valid right-hand side formula
643 if (rhs) {
644 if (errorFlag) {
645 addError(expr, ValidationError.AX_RHS_ERR + error);
646 }
647 }
648 else if (lhs) {
649 if (errorFlag) {
650 addError(expr, ValidationError.AX_LHS_ERR + error);
651 }
652 }
653 else {
654 LogicalExpression left = expr.getLeftOperand();
655 LogicalExpression right = expr.getRightOperand();
656 InverseImplication invImp = leFactory.createInverseImplication(right, left);
657 invImp.accept(this);
658 }
659 }
660
661 /**
662 * Checks if an Equivalence is valid to wsml-core.
663 *
664 * @see org.deri.wsmo4j.validator.WsmlFlightExpressionValidator#visitEquivalence(org.omwg.logicalexpression.Equivalence)
665 */
666 public void visitEquivalence(Equivalence expr) {
667 String error = ":\n Cannot contain an Equivalence:\n"
668 + leSerializer.serialize(expr);
669 // An Equivalence is no valid right-hand side formula
670 if (rhs) {
671 if (errorFlag) {
672 addError(expr, ValidationError.AX_RHS_ERR + error);
673 }
674 }
675 else if (lhs) {
676 if (errorFlag) {
677 addError(expr, ValidationError.AX_LHS_ERR + error);
678 }
679 }
680 else {
681 equivVariables.clear();
682 rhs = true;
683 expr.getLeftOperand().accept(this);
684 expr.getRightOperand().accept(this);
685
686 if (equivVariables.size() > 1) {
687 addError(expr, ValidationError.AX_EQUIV_ERR + ": The Equivalence formula " +
688 "can only contain one variable\n" + leSerializer.serialize(expr));
689 equivVariables.clear();
690 }
691 equivVariables.clear();
692 }
693 }
694
695 /**
696 * Checks if a LogicProgrammingRule is valid to wsml-core.
697 *
698 * @see org.deri.wsmo4j.validator.WsmlFlightExpressionValidator#visitLogicProgrammingRule(org.omwg.logicalexpression.LogicProgrammingRule)
699 */
700 public void visitLogicProgrammingRule(LogicProgrammingRule expr) {
701 String error = ":\n Cannot contain a LogicProgrammingRule:\n"
702 + leSerializer.serialize(expr);
703 // A LogicProgrammingRule is no valid right-hand side formula
704 if (rhs) {
705 if (errorFlag) {
706 addError(expr, ValidationError.AX_RHS_ERR + error);
707 }
708 }
709 else if (lhs) {
710 if (errorFlag) {
711 addError(expr, ValidationError.AX_LHS_ERR + error);
712 }
713 }
714 else {
715 addError(expr, ValidationError.AX_FORMULA_ERR + ": A LogicProgrammingRule" +
716 " is not a valid formula\n" + leSerializer.serialize(expr));
717 }
718 }
719
720 /**
721 * Checks if a UniversalQuantification is valid to wsml-core.
722 *
723 * @see org.deri.wsmo4j.validator.WsmlFlightExpressionValidator#visitUniversalQuantification(org.omwg.logicalexpression.UniversalQuantification)
724 */
725 public void visitUniversalQuantification(UniversalQuantification expr) {
726 String error = ":\n Cannot contain an UniversalQuantification:\n"
727 + leSerializer.serialize(expr);
728 // An UniversalQuantification is no valid right-hand side formula
729 if (rhs) {
730 if (errorFlag) {
731 addError(expr, ValidationError.AX_RHS_ERR + error);
732 }
733 }
734 else if (lhs) {
735 if (errorFlag) {
736 addError(expr, ValidationError.AX_LHS_ERR + error);
737 }
738 }
739 else {
740 addError(expr, ValidationError.AX_FORMULA_ERR + ": A UniversalQuantification" +
741 " is not a valid formula\n" + leSerializer.serialize(expr));
742 }
743 }
744
745 /**
746 * Checks if an ExistentialQuantification is valid to wsml-core.
747 *
748 * @see org.deri.wsmo4j.validator.WsmlFlightExpressionValidator#visitExistentialQuantification(org.omwg.logicalexpression.ExistentialQuantification)
749 */
750 public void visitExistentialQuantification(ExistentialQuantification expr) {
751 String error = ":\n Cannot contain an ExistentialQuantification:\n"
752 + leSerializer.serialize(expr);
753 // An ExistentialQuantification is no valid right-hand side formula
754 if (rhs) {
755 if (errorFlag) {
756 addError(expr, ValidationError.AX_RHS_ERR + error);
757 }
758 }
759 else if (lhs) {
760 if (errorFlag) {
761 addError(expr, ValidationError.AX_LHS_ERR + error);
762 }
763 }
764 else {
765 addError(expr, ValidationError.AX_FORMULA_ERR + ":\n A ExistentialQuantification" +
766 " is not a valid formula\n" + leSerializer.serialize(expr));
767 }
768 }
769
770 /*
771 * Gets an atom and transforms it into a value definition molecule
772 */
773 private Molecule atomToMolecule(Atom expr) {
774 Molecule molecule = null;
775 // the atom must be a binary atom
776 if (expr.getArity() != 2) {
777 addError(expr, ValidationError.AX_ATOMIC_ERR + ":\nThe atom must " +
778 "be a binary atom\n" + leSerializer.serialize(expr));
779 return molecule;
780 }
781 else {
782 molecule = leFactory.createAttributeValue(
783 expr.getParameter(0), expr.getIdentifier(), expr.getParameter(1));
784
785 return molecule;
786 }
787 }
788
789 /*
790 * Checks if a specified InverseImplication, containing a molecule and a
791 * conjunction as operands, is a valid transitive construction
792 */
793 private void isValidTransitiveInvImpl(InverseImplication expr) {
794 AttributeValueMolecule left = null;
795 AttributeValueMolecule conLeft = null;
796 AttributeValueMolecule conRight = null;
797 LogicalExpression l = expr.getLeftOperand();
798 LogicalExpression cLeft = ((Conjunction) expr.getRightOperand()).getLeftOperand();
799 LogicalExpression cRight = ((Conjunction) expr.getRightOperand()).getRightOperand();
800 if (l instanceof Atom) {
801 left = (AttributeValueMolecule) atomToMolecule((Atom) l);
802 }
803 else {
804 left = (AttributeValueMolecule) l;
805 }
806 if (cLeft instanceof Atom) {
807 conLeft = (AttributeValueMolecule) atomToMolecule((Atom) cLeft);
808 }
809 else {
810 conLeft = (AttributeValueMolecule) cLeft;
811 }
812 if (cRight instanceof Atom) {
813 conRight = (AttributeValueMolecule) atomToMolecule((Atom) cRight);
814 }
815 else{
816 conRight = (AttributeValueMolecule) cRight;
817 }
818 if (left == null || conLeft == null || conRight == null) {
819 addError(expr, ValidationError.AX_IMPL_BY_ERR + ": Invalid atom\n" +
820 leSerializer.serialize(expr));
821 return;
822 }
823
824 rhs = false;
825 lhs = false;
826 formula = true;
827 left.accept(this);
828 conLeft.accept(this);
829 conRight.accept(this);
830
831 if (left.getLeftParameter() instanceof Variable
832 && conLeft.getLeftParameter() instanceof Variable
833 && conRight.getLeftParameter() instanceof Variable
834 && left.getRightParameter() instanceof Variable
835 && conLeft.getRightParameter() instanceof Variable
836 && conRight.getRightParameter() instanceof Variable
837 && left.getAttribute() instanceof Term
838 && conLeft.getAttribute() instanceof Term
839 && conRight.getAttribute() instanceof Term) {
840 Variable leftTerm = (Variable) left.getLeftParameter();
841 Variable conLeftTerm = (Variable) conLeft.getLeftParameter();
842 Variable conRightTerm = (Variable) conRight.getLeftParameter();
843 Term leftRel = left.getAttribute();
844 Term conLeftRel = conLeft.getAttribute();
845 Term conRightRel = conRight.getAttribute();
846 Variable leftArg = (Variable) left.getRightParameter();
847 Variable conLeftArg = (Variable) conLeft.getRightParameter();
848 Variable conRightArg = (Variable) conRight.getRightParameter();
849
850 // check on globally transitive attribute/relation
851 if (leftTerm.equals(conLeftTerm) && leftTerm.equals(conRightTerm)) {
852 addError(expr, ValidationError.AX_IMPL_BY_ERR + ": The molecule's " +
853 "term must be contained in exactly one of the conjunction's " +
854 "molecule's terms\n" + leSerializer.serialize(expr));
855 }
856 else if (!(leftRel.equals(conLeftRel)) || !(leftRel.equals(conRightRel))) {
857 addError(expr, ValidationError.AX_IMPL_BY_ERR + ": The molecule's " +
858 "attribute's names must be equal\n" + leSerializer.serialize(expr));
859 }
860 else if (leftTerm.equals(conLeftTerm)) {
861 if (!(leftArg.equals(conRightArg)) || !(conLeftArg.equals(conRightTerm))) {
862 addError(expr, ValidationError.AX_IMPL_BY_ERR + ": No valid" +
863 " transitive construction\n" + leSerializer.serialize(expr));
864 }
865 }
866 else if (leftTerm.equals(conRightTerm)) {
867 if (!(leftArg.equals(conLeftArg)) || !(conRightArg.equals(conLeftTerm))) {
868 addError(expr, ValidationError.AX_IMPL_BY_ERR + ": No valid" +
869 " transitive construction\n" + leSerializer.serialize(expr));
870 }
871 }
872 }
873 }
874
875 /*
876 * Checks if an Inverse Implication, containing two molecules as Operands,
877 * is a valid construction. Valid constructions are symmetric, sub-attribute
878 * and inverse attribute structures
879 */
880 private void isValidInverseImplication(InverseImplication expr) {
881 AttributeValueMolecule left = null;
882 AttributeValueMolecule right = null;
883 LogicalExpression l = expr.getLeftOperand();
884 LogicalExpression r = expr.getRightOperand();
885 if (l instanceof Atom) {
886 left = (AttributeValueMolecule) atomToMolecule((Atom) l);
887 }
888 else {
889 left = (AttributeValueMolecule) l;
890 }
891 if (r instanceof Atom) {
892 right = (AttributeValueMolecule) atomToMolecule((Atom) r);
893 }
894 else {
895 right = (AttributeValueMolecule) r;
896 }
897 if (left == null || right == null) {
898 addError(expr, ValidationError.AX_IMPL_BY_ERR + ": Invalid atom" +
899 leSerializer.serialize(expr));
900 return;
901 }
902 errorFlag = true;
903 rhs = false;
904 lhs = false;
905 formula = true;
906 left.accept(this);
907 right.accept(this);
908
909 if (left.getLeftParameter() instanceof Variable
910 && right.getLeftParameter() instanceof Variable
911 && left.getRightParameter() instanceof Variable
912 && right.getRightParameter() instanceof Variable
913 && left.getAttribute() instanceof Term
914 && right.getAttribute() instanceof Term) {
915
916 Variable leftTerm = (Variable) left.getLeftParameter();
917 Variable rightTerm = (Variable) right.getLeftParameter();
918 Term leftRel = left.getAttribute();
919 Term rightRel = right.getAttribute();
920 Variable leftArg = (Variable) left.getRightParameter();
921 Variable rightArg = (Variable) right.getRightParameter();
922
923 // check on globally symmetric and inverse attribute/relation
924 if (!(leftTerm.equals(rightArg)) || !(leftArg.equals(rightTerm))) {
925
926 // check on globally sub-attribute/relation
927 if (!(leftTerm.equals(rightTerm)) || !(leftArg.equals(rightArg)) || leftRel.equals(rightRel)) {
928 addError(expr, ValidationError.AX_IMPL_BY_ERR + ": No valid" +
929 " symmetric, sub-attribute or inverse construction\n" +
930 leSerializer.serialize(expr));
931 }
932 }
933 }
934 }
935
936 /*
937 * Check if a specified Molecule's parameter or a term is used in the actual
938 * axiom as Instance, Relation or Datatype, or whether it is a Variable
939 */
940 private boolean check(Object o, boolean concept, boolean instance,
941 boolean relation, boolean datatype, boolean variable) {
942 if (o instanceof Molecule) {
943 if (concept && checkConcepts(((Molecule) o).getLeftParameter())) {
944 error = "Concept";
945 return true;
946 }
947 if (instance && checkInstances(((Molecule) o).getLeftParameter())) {
948 error = "Instance";
949 return true;
950 }
951 else if (relation && checkRelations(((Molecule) o).getLeftParameter())) {
952 error = "Relation";
953 return true;
954 }
955 else if (datatype && checkDatatypes(((Molecule) o).getLeftParameter())) {
956 error = "Datatype";
957 return true;
958 }
959 else if (variable && (((Molecule) o).getLeftParameter() instanceof Variable)) {
960 error = "Variable";
961 return true;
962 }
963 }
964 else if (o instanceof Term) {
965 if (concept && checkConcepts(o)) {
966 error = "Concept";
967 }
968 if (instance && checkInstances(o)) {
969 error = "Instance";
970 return true;
971 }
972 else if (relation && checkRelations(o)) {
973 error = "Relation";
974 return true;
975 }
976 else if (datatype && checkDatatypes(o)) {
977 error = "Datatype";
978 return true;
979 }
980 else if (variable && (o instanceof Variable)) {
981 error = "Variable";
982 return true;
983 }
984 }
985 return false;
986 }
987
988 /*
989 * Checks if a specified Term is contained in the concepts vector
990 */
991 private boolean checkConcepts(Object o) {
992 return validator.getIdConcepts().contains(o);
993 }
994
995 /*
996 * Checks if a specified Term is contained in the instances vector
997 */
998 private boolean checkInstances(Object o) {
999 return validator.getIdInstances().contains(o);
1000 }
1001
1002 /*
1003 * Checks if a specified Term is contained in the relations vector
1004 */
1005 private boolean checkRelations(Object o) {
1006 return validator.getIdRelations().contains(o);
1007 }
1008
1009 /*
1010 * Checks if a specified Term is contained in the abstract relations vector
1011 */
1012 private boolean checkAbstractRelations(Object o) {
1013 return validator.getIdAbstractRelations().contains(o);
1014 }
1015
1016 /*
1017 * Checks if a specified Term is contained in the concrete relations vector
1018 */
1019 private boolean checkConcreteRelations(Object o) {
1020 return validator.getIdConcreteRelations().contains(o);
1021 }
1022
1023 /*
1024 * Checks if a specified Term is contained in the datatypes vector
1025 */
1026 private boolean checkDatatypes(Object o) {
1027 return ConstantTransformer.getInstance().isDataType(o.toString());
1028 }
1029
1030 public int getNumberOfMolecules() {
1031 return numberOfMolecules;
1032 }
1033
1034 public Set getLHSVariables() {
1035 return lhsVariables;
1036 }
1037
1038 /*
1039 * Adds a new ValidationError to the error list
1040 */
1041 private void addError(LogicalExpression logexp, String msg) {
1042 LogicalExpressionErrorImpl le = new LogicalExpressionErrorImpl(
1043 axiom, logexp, msg, WSML.WSML_CORE);
1044 if (!errors.contains(le)) {
1045 errors.add(le);
1046 }
1047 }
1048
1049 protected class Graph {
1050
1051 private Map <Variable, List <Variable>> listMap = new HashMap <Variable, List <Variable>> ();
1052 private List <Variable> connected = new Vector <Variable> ();
1053
1054 /*
1055 * Checks if the variables and molecules of a given inverse implication
1056 * build a valid connected and acyclic graph.
1057 */
1058 protected boolean isValidGraph(Binary expr) {
1059 listMap.clear();
1060 connected.clear();
1061
1062 buildLists();
1063
1064 Iterator it = lhsVariables.iterator();
1065 Variable v1 = (Variable) it.next();
1066 Variable v = null;
1067 boolean valid = false;
1068
1069 // check if the given graph is connected
1070 while(it.hasNext()) {
1071 v = (Variable) it.next();
1072 valid = checkGraphConnected(v1, v);
1073 if (!valid) {
1074 addError(expr, ValidationError.AX_GRAPH_ERR + ":\nGraph is " +
1075 "not connected:\n" + leSerializer.serialize(expr));
1076 return false;
1077 }
1078 }
1079
1080 // check if the given graph is acyclic
1081 List <Variable> checkList = new Vector <Variable> ();
1082 checkList.add(v1);
1083 valid = checkGraphAcyclic(v1, v1, checkList);
1084 if (valid) {
1085 return true;
1086 }
1087 else {
1088 addError(expr, ValidationError.AX_GRAPH_ERR + ":\nGraph contains " +
1089 "cycle:\n" + leSerializer.serialize(expr));
1090 return false;
1091 }
1092 }
1093
1094 /*
1095 * Build a Map with a specific variable as key and with a list as value,
1096 * that contains all variables to which the key variable is connected.
1097 */
1098 private void buildLists() {
1099 Variable v1 = null;
1100 Variable v = null;
1101
1102 Iterator it = lhsVariables.iterator();
1103 while (it.hasNext()) {
1104 List <Variable> list = new Vector <Variable> ();
1105 v1 = (Variable) it.next();
1106 Iterator itMol = molecules.iterator();
1107 while (itMol.hasNext()) {
1108 List l = (List) itMol.next();
1109 if (l.get(0).equals(v1)) {
1110 v = (Variable) l.get(1);
1111 list.add(v);
1112 }
1113 else if (l.get(1).equals(v1)) {
1114 v = (Variable) l.get(0);
1115 list.add(v);
1116 }
1117 }
1118 listMap.put(v1, list);
1119 }
1120 }
1121
1122 /*
1123 * Checks if variable v1 is connected to variable v2.
1124 */
1125 private boolean checkGraphConnected(Variable v1, Variable v2) {
1126 boolean found = false;
1127 boolean used = false;
1128
1129 List <Variable> l = listMap.get(v1);
1130
1131 if (l.contains(v2)) {
1132 return true;
1133 }
1134 else {
1135 connected.add(v1);
1136 Iterator it = l.iterator();
1137 while (it.hasNext()) {
1138 Variable v = (Variable) it.next();
1139 for (int i=0; i<connected.size(); i++) {
1140 if (v.equals(connected.get(i))) {
1141 used = true;
1142 }
1143 }
1144 if (!used) {
1145 found = checkGraphConnected(v, v2);
1146 }
1147 if (found) {
1148 return true;
1149 }
1150 used = false;
1151 }
1152 return false;
1153 }
1154 }
1155
1156 /*
1157 * Checks if a given graph contains a cycle.
1158 */
1159 private boolean checkGraphAcyclic(Variable from, Variable v, List checkList) {
1160 if ((numberOfMolecules + 1) == lhsVariables.size()) {
1161 return true;
1162 }
1163 else {
1164 return false;
1165 }
1166 }
1167 }
1168
1169 }
|
{
"url": "http://wsmo4j.sourceforge.net/wsmo4j/xref/org/deri/wsmo4j/validator/WsmlCoreExpressionValidator.html",
"source_domain": "wsmo4j.sourceforge.net",
"snapshot_id": "crawl=CC-MAIN-2018-13",
"warc_metadata": {
"Content-Length": "120278",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:HEEPMJPYF64ZVUYZUFFKDC6NTODRHB6F",
"WARC-Concurrent-To": "<urn:uuid:e974103b-42fb-4076-862c-f1fdfea5f430>",
"WARC-Date": "2018-03-20T21:24:59Z",
"WARC-IP-Address": "216.105.38.10",
"WARC-Identified-Payload-Type": "application/xhtml+xml",
"WARC-Payload-Digest": "sha1:RPGSXJ76YUUKSHJZ5DAWS5R6F54L7SUA",
"WARC-Record-ID": "<urn:uuid:de3d4738-a714-4ca4-8633-2deb5c152ea8>",
"WARC-Target-URI": "http://wsmo4j.sourceforge.net/wsmo4j/xref/org/deri/wsmo4j/validator/WsmlCoreExpressionValidator.html",
"WARC-Truncated": "length",
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:940411f0-9026-4edf-b1f6-c2f5e7099710>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-149-106-148.ec2.internal\r\nsoftware: Nutch 1.6 (CC)\r\nisPartOf: CC-MAIN-2018-13\r\noperator: Common Crawl Admin\r\ndescription: Wide crawl of the web for March 2018\r\npublisher: Common Crawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
13,
14,
21,
75,
133,
216,
297,
378,
402,
483,
566,
648,
662,
746,
823,
882,
890,
929,
934,
964,
994,
1025,
1052,
1078,
1104,
1133,
1138,
1207,
1273,
1317,
1373,
1440,
1506,
1568,
1614,
1670,
1721,
1771,
1822,
1873,
1938,
1989,
2047,
2107,
2164,
2222,
2270,
2318,
2375,
2433,
2496,
2543,
2593,
2629,
2668,
2701,
2755,
2802,
2807,
2812,
2820,
2878,
2885,
2898,
2930,
2969,
2987,
3001,
3008,
3051,
3139,
3147,
3193,
3225,
3230,
3280,
3289,
3337,
3346,
3394,
3403,
3446,
3455,
3507,
3516,
3568,
3577,
3636,
3645,
3704,
3713,
3749,
3758,
3812,
3821,
3851,
3860,
3893,
3902,
3931,
3940,
3969,
3978,
4013,
4022,
4031,
4043,
4103,
4201,
4213,
4364,
4396,
4430,
4464,
4515,
4555,
4565,
4570,
4603,
4653,
4688,
4742,
4794,
4844,
4894,
4923,
4948,
4973,
5003,
5013,
5022,
5034,
5086,
5098,
5213,
5225,
5268,
5322,
5358,
5397,
5411,
5421,
5426,
5438,
5513,
5525,
5685,
5697,
5785,
5868,
5916,
5998,
6027,
6060,
6133,
6151,
6165,
6193,
6226,
6298,
6316,
6330,
6349,
6401,
6486,
6557,
6634,
6719,
6737,
6788,
6874,
6945,
7004,
7099,
7117,
7196,
7276,
7352,
7424,
7510,
7595,
7614,
7628,
7638,
7643,
7655,
7729,
7741,
7900,
7912,
7999,
8081,
8129,
8210,
8239,
8272,
8344,
8362,
8376,
8404,
8437,
8509,
8527,
8541,
8560,
8612,
8697,
8768,
8845,
8930,
8948,
9036,
9123,
9213,
9277,
9360,
9382,
9406,
9520,
9588,
9664,
9757,
9837,
9950,
9976,
9998,
10111,
10183,
10259,
10352,
10432,
10544,
10570,
10592,
10610,
10624,
10634,
10639,
10651,
10721,
10733,
10884,
10896,
10975,
11052,
11081,
11114,
11194,
11262,
11323,
11341,
11355,
11427,
11461,
11530,
11600,
11637,
11735,
11842,
11864,
11892,
11910,
11986,
12049,
12067,
12084,
12148,
12216,
12253,
12353,
12444,
12509,
12531,
12559,
12577,
12592,
12660,
12731,
12768,
12868,
12977,
12999,
13027,
13045,
13122,
13186,
13204,
13227,
13281,
13329,
13410,
13463,
13481,
13540,
13574,
13588,
13607,
13661,
13746,
13818,
13897,
13982,
14000,
14097,
14184,
14273,
14339,
14422,
14440,
14463,
14578,
14646,
14722,
14815,
14895,
15009,
15035,
15057,
15172,
15245,
15321,
15414,
15494,
15608,
15634,
15656,
15674,
15688,
15698,
15703,
15715,
15778,
15789,
15928,
15940,
16007,
16064,
16096,
16147,
16161,
16171,
16176,
16188,
16253,
16264,
16407,
16419,
16490,
16558,
16581,
16650,
16720,
16757,
16857,
16964,
16986,
17004,
17027,
17104,
17173,
17195,
17270,
17337,
17359,
17377,
17443,
17529,
17566,
17643,
17738,
17803,
17825,
17843,
17857,
17885,
17918,
17998,
18061,
18122,
18140,
18154,
18173,
18227,
18312,
18384,
18457,
18542,
18560,
18610,
18696,
18767,
18836,
18919,
18937,
18951,
18961,
18966,
18978,
19043,
19054,
19197,
19209,
19280,
19353,
19401,
19473,
19502,
19535,
19607,
19625,
19639,
19667,
19700,
19772,
19790,
19804,
19823,
19851,
19903,
19988,
20059,
20130,
20215,
20233,
20283,
20369,
20440,
20509,
20592,
20610,
20624,
20634,
20641,
20653,
20708,
20720,
20843,
20855,
20906,
20969,
21017,
21079,
21102,
21135,
21207,
21225,
21239,
21267,
21300,
21372,
21390,
21404,
21423,
21507,
21590,
21604,
21614,
21619,
21631,
21695,
21707,
21848,
21860,
21929,
22001,
22049,
22120,
22143,
22176,
22248,
22266,
22280,
22308,
22341,
22413,
22431,
22445,
22464,
22555,
22640,
22654,
22664,
22669,
22681,
22738,
22750,
22877,
22889,
22944,
23009,
23057,
23121,
23144,
23177,
23249,
23267,
23281,
23309,
23342,
23414,
23432,
23446,
23465,
23556,
23634,
23648,
23658,
23663,
23675,
23733,
23745,
23874,
23886,
23943,
24017,
24047,
24099,
24152,
24166,
24185,
24252,
24333,
24390,
24408,
24431,
24514,
24594,
24668,
24686,
24754,
24836,
24893,
24911,
24934,
25017,
25097,
25171,
25189,
25203,
25213,
25218,
25230,
25288,
25300,
25429,
25441,
25498,
25563,
25586,
25619,
25699,
25787,
25805,
25819,
25902,
25930,
25982,
26035,
26049,
26068,
26160,
26238,
26252,
26262,
26267,
26279,
26345,
26357,
26500,
26512,
26583,
26657,
26705,
26778,
26801,
26834,
26906,
26924,
26938,
26966,
26999,
27071,
27089,
27103,
27122,
27160,
27198,
27233,
27301,
27367,
27372,
27431,
27476,
27548,
27605,
27700,
27797,
27856,
27940,
28007,
28094,
28149,
28170,
28187,
28271,
28368,
28465,
28517,
28534,
28556,
28638,
28676,
28709,
28747,
28779,
28810,
28849,
28881,
28901,
28959,
29001,
29065,
29151,
29229,
29331,
29356,
29377,
29427,
29477,
29526,
29547,
29564,
29578,
29588,
29593,
29605,
29664,
29676,
29805,
29817,
29874,
29941,
29989,
30055,
30078,
30111,
30183,
30201,
30215,
30243,
30276,
30348,
30366,
30380,
30399,
30463,
30529,
30622,
30659,
30673,
30683,
30688,
30700,
30759,
30771,
30900,
30912,
30969,
31036,
31084,
31150,
31173,
31206,
31278,
31296,
31310,
31338,
31371,
31443,
31461,
31475,
31494,
31534,
31562,
31614,
31667,
31672,
31721,
31818,
31913,
31957,
31975,
32015,
32029,
32039,
32044,
32056,
32123,
32135,
32282,
32294,
32369,
32444,
32492,
32566,
32589,
32622,
32694,
32712,
32726,
32754,
32787,
32859,
32877,
32891,
32910,
33003,
33089,
33103,
33113,
33118,
33130,
33200,
33212,
33365,
33377,
33458,
33537,
33585,
33663,
33686,
33719,
33791,
33809,
33823,
33851,
33884,
33956,
33974,
33988,
34007,
34103,
34189,
34203,
34213,
34218,
34230,
34303,
34315,
34472,
34484,
34569,
34650,
34698,
34778,
34801,
34834,
34906,
34924,
34938,
34966,
34999,
35071,
35089,
35103,
35122,
35222,
35308,
35322,
35332,
35341,
35352,
35427,
35439,
35492,
35530,
35576,
35616,
35701,
35779,
35812,
35826,
35845,
35904,
35995,
36012,
36045,
36059,
36069,
36081,
36092,
36174,
36245,
36257,
36330,
36378,
36429,
36481,
36538,
36633,
36730,
36767,
36841,
36855,
36874,
36925,
36939,
36980,
37061,
37075,
37094,
37152,
37166,
37208,
37291,
37305,
37323,
37383,
37397,
37468,
37553,
37608,
37632,
37646,
37651,
37676,
37701,
37729,
37760,
37794,
37829,
37842,
37903,
37973,
38044,
38112,
38183,
38255,
38314,
38376,
38442,
38514,
38592,
38672,
38724,
38782,
38847,
38919,
38997,
39077,
39094,
39161,
39246,
39336,
39428,
39510,
39528,
39620,
39710,
39807,
39825,
39882,
39978,
40065,
40159,
40181,
40199,
40257,
40352,
40439,
40533,
40555,
40573,
40587,
40597,
40606,
40617,
40701,
40787,
40831,
40843,
40917,
40965,
41014,
41071,
41129,
41166,
41240,
41254,
41273,
41324,
41338,
41375,
41450,
41464,
41483,
41535,
41549,
41598,
41681,
41736,
41760,
41774,
41804,
41829,
41854,
41882,
41913,
41945,
41958,
42019,
42087,
42155,
42224,
42283,
42346,
42360,
42432,
42506,
42558,
42619,
42691,
42765,
42786,
42864,
42948,
42969,
43033,
43149,
43236,
43325,
43388,
43411,
43429,
43443,
43453,
43462,
43473,
43559,
43639,
43651,
43727,
43799,
43840,
43923,
43962,
43995,
44013,
44098,
44138,
44171,
44189,
44279,
44319,
44352,
44370,
44460,
44500,
44533,
44551,
44647,
44687,
44720,
44738,
44752,
44794,
44845,
44884,
44902,
44955,
44995,
45028,
45046,
45104,
45144,
45177,
45195,
45253,
45293,
45326,
45344,
45408,
45448,
45481,
45499,
45513,
45539,
45549,
45558,
45569,
45643,
45655,
45705,
45763,
45773,
45782,
45793,
45868,
45880,
45931,
45990,
46001,
46011,
46023,
46099,
46112,
46164,
46224,
46235,
46245,
46257,
46342,
46355,
46415,
46483,
46494,
46504,
46516,
46601,
46614,
46674,
46742,
46753,
46763,
46775,
46851,
46864,
46916,
46996,
47007,
47013,
47058,
47097,
47108,
47114,
47154,
47188,
47199,
47209,
47221,
47278,
47291,
47362,
47439,
47497,
47538,
47571,
47586,
47597,
47607,
47636,
47650,
47757,
47832,
47846,
47862,
47947,
48006,
48023,
48088,
48122,
48158,
48176,
48207,
48221,
48277,
48330,
48366,
48406,
48424,
48482,
48521,
48575,
48632,
48667,
48755,
48840,
48879,
48902,
48921,
48939,
48997,
49068,
49104,
49167,
49197,
49231,
49250,
49274,
49364,
49437,
49472,
49491,
49506,
49520,
49536,
49623,
49707,
49724,
49765,
49802,
49838,
49856,
49912,
49952,
50022,
50070,
50130,
50177,
50232,
50284,
50338,
50380,
50408,
50465,
50519,
50561,
50590,
50613,
50657,
50676,
50691,
50705,
50721,
50788,
50805,
50882,
50922,
50961,
50979,
51033,
51051,
51090,
51124,
51143,
51167,
51207,
51256,
51300,
51361,
51427,
51490,
51536,
51567,
51594,
51632,
51697,
51724,
51762,
51804,
51831,
51870,
51893,
51928,
51947,
51962,
51979,
51995,
52054,
52071,
52163,
52234,
52268,
52287,
52311,
52346,
52365,
52380,
52391,
52401
],
"line_end_idx": [
13,
14,
21,
75,
133,
216,
297,
378,
402,
483,
566,
648,
662,
746,
823,
882,
890,
929,
934,
964,
994,
1025,
1052,
1078,
1104,
1133,
1138,
1207,
1273,
1317,
1373,
1440,
1506,
1568,
1614,
1670,
1721,
1771,
1822,
1873,
1938,
1989,
2047,
2107,
2164,
2222,
2270,
2318,
2375,
2433,
2496,
2543,
2593,
2629,
2668,
2701,
2755,
2802,
2807,
2812,
2820,
2878,
2885,
2898,
2930,
2969,
2987,
3001,
3008,
3051,
3139,
3147,
3193,
3225,
3230,
3280,
3289,
3337,
3346,
3394,
3403,
3446,
3455,
3507,
3516,
3568,
3577,
3636,
3645,
3704,
3713,
3749,
3758,
3812,
3821,
3851,
3860,
3893,
3902,
3931,
3940,
3969,
3978,
4013,
4022,
4031,
4043,
4103,
4201,
4213,
4364,
4396,
4430,
4464,
4515,
4555,
4565,
4570,
4603,
4653,
4688,
4742,
4794,
4844,
4894,
4923,
4948,
4973,
5003,
5013,
5022,
5034,
5086,
5098,
5213,
5225,
5268,
5322,
5358,
5397,
5411,
5421,
5426,
5438,
5513,
5525,
5685,
5697,
5785,
5868,
5916,
5998,
6027,
6060,
6133,
6151,
6165,
6193,
6226,
6298,
6316,
6330,
6349,
6401,
6486,
6557,
6634,
6719,
6737,
6788,
6874,
6945,
7004,
7099,
7117,
7196,
7276,
7352,
7424,
7510,
7595,
7614,
7628,
7638,
7643,
7655,
7729,
7741,
7900,
7912,
7999,
8081,
8129,
8210,
8239,
8272,
8344,
8362,
8376,
8404,
8437,
8509,
8527,
8541,
8560,
8612,
8697,
8768,
8845,
8930,
8948,
9036,
9123,
9213,
9277,
9360,
9382,
9406,
9520,
9588,
9664,
9757,
9837,
9950,
9976,
9998,
10111,
10183,
10259,
10352,
10432,
10544,
10570,
10592,
10610,
10624,
10634,
10639,
10651,
10721,
10733,
10884,
10896,
10975,
11052,
11081,
11114,
11194,
11262,
11323,
11341,
11355,
11427,
11461,
11530,
11600,
11637,
11735,
11842,
11864,
11892,
11910,
11986,
12049,
12067,
12084,
12148,
12216,
12253,
12353,
12444,
12509,
12531,
12559,
12577,
12592,
12660,
12731,
12768,
12868,
12977,
12999,
13027,
13045,
13122,
13186,
13204,
13227,
13281,
13329,
13410,
13463,
13481,
13540,
13574,
13588,
13607,
13661,
13746,
13818,
13897,
13982,
14000,
14097,
14184,
14273,
14339,
14422,
14440,
14463,
14578,
14646,
14722,
14815,
14895,
15009,
15035,
15057,
15172,
15245,
15321,
15414,
15494,
15608,
15634,
15656,
15674,
15688,
15698,
15703,
15715,
15778,
15789,
15928,
15940,
16007,
16064,
16096,
16147,
16161,
16171,
16176,
16188,
16253,
16264,
16407,
16419,
16490,
16558,
16581,
16650,
16720,
16757,
16857,
16964,
16986,
17004,
17027,
17104,
17173,
17195,
17270,
17337,
17359,
17377,
17443,
17529,
17566,
17643,
17738,
17803,
17825,
17843,
17857,
17885,
17918,
17998,
18061,
18122,
18140,
18154,
18173,
18227,
18312,
18384,
18457,
18542,
18560,
18610,
18696,
18767,
18836,
18919,
18937,
18951,
18961,
18966,
18978,
19043,
19054,
19197,
19209,
19280,
19353,
19401,
19473,
19502,
19535,
19607,
19625,
19639,
19667,
19700,
19772,
19790,
19804,
19823,
19851,
19903,
19988,
20059,
20130,
20215,
20233,
20283,
20369,
20440,
20509,
20592,
20610,
20624,
20634,
20641,
20653,
20708,
20720,
20843,
20855,
20906,
20969,
21017,
21079,
21102,
21135,
21207,
21225,
21239,
21267,
21300,
21372,
21390,
21404,
21423,
21507,
21590,
21604,
21614,
21619,
21631,
21695,
21707,
21848,
21860,
21929,
22001,
22049,
22120,
22143,
22176,
22248,
22266,
22280,
22308,
22341,
22413,
22431,
22445,
22464,
22555,
22640,
22654,
22664,
22669,
22681,
22738,
22750,
22877,
22889,
22944,
23009,
23057,
23121,
23144,
23177,
23249,
23267,
23281,
23309,
23342,
23414,
23432,
23446,
23465,
23556,
23634,
23648,
23658,
23663,
23675,
23733,
23745,
23874,
23886,
23943,
24017,
24047,
24099,
24152,
24166,
24185,
24252,
24333,
24390,
24408,
24431,
24514,
24594,
24668,
24686,
24754,
24836,
24893,
24911,
24934,
25017,
25097,
25171,
25189,
25203,
25213,
25218,
25230,
25288,
25300,
25429,
25441,
25498,
25563,
25586,
25619,
25699,
25787,
25805,
25819,
25902,
25930,
25982,
26035,
26049,
26068,
26160,
26238,
26252,
26262,
26267,
26279,
26345,
26357,
26500,
26512,
26583,
26657,
26705,
26778,
26801,
26834,
26906,
26924,
26938,
26966,
26999,
27071,
27089,
27103,
27122,
27160,
27198,
27233,
27301,
27367,
27372,
27431,
27476,
27548,
27605,
27700,
27797,
27856,
27940,
28007,
28094,
28149,
28170,
28187,
28271,
28368,
28465,
28517,
28534,
28556,
28638,
28676,
28709,
28747,
28779,
28810,
28849,
28881,
28901,
28959,
29001,
29065,
29151,
29229,
29331,
29356,
29377,
29427,
29477,
29526,
29547,
29564,
29578,
29588,
29593,
29605,
29664,
29676,
29805,
29817,
29874,
29941,
29989,
30055,
30078,
30111,
30183,
30201,
30215,
30243,
30276,
30348,
30366,
30380,
30399,
30463,
30529,
30622,
30659,
30673,
30683,
30688,
30700,
30759,
30771,
30900,
30912,
30969,
31036,
31084,
31150,
31173,
31206,
31278,
31296,
31310,
31338,
31371,
31443,
31461,
31475,
31494,
31534,
31562,
31614,
31667,
31672,
31721,
31818,
31913,
31957,
31975,
32015,
32029,
32039,
32044,
32056,
32123,
32135,
32282,
32294,
32369,
32444,
32492,
32566,
32589,
32622,
32694,
32712,
32726,
32754,
32787,
32859,
32877,
32891,
32910,
33003,
33089,
33103,
33113,
33118,
33130,
33200,
33212,
33365,
33377,
33458,
33537,
33585,
33663,
33686,
33719,
33791,
33809,
33823,
33851,
33884,
33956,
33974,
33988,
34007,
34103,
34189,
34203,
34213,
34218,
34230,
34303,
34315,
34472,
34484,
34569,
34650,
34698,
34778,
34801,
34834,
34906,
34924,
34938,
34966,
34999,
35071,
35089,
35103,
35122,
35222,
35308,
35322,
35332,
35341,
35352,
35427,
35439,
35492,
35530,
35576,
35616,
35701,
35779,
35812,
35826,
35845,
35904,
35995,
36012,
36045,
36059,
36069,
36081,
36092,
36174,
36245,
36257,
36330,
36378,
36429,
36481,
36538,
36633,
36730,
36767,
36841,
36855,
36874,
36925,
36939,
36980,
37061,
37075,
37094,
37152,
37166,
37208,
37291,
37305,
37323,
37383,
37397,
37468,
37553,
37608,
37632,
37646,
37651,
37676,
37701,
37729,
37760,
37794,
37829,
37842,
37903,
37973,
38044,
38112,
38183,
38255,
38314,
38376,
38442,
38514,
38592,
38672,
38724,
38782,
38847,
38919,
38997,
39077,
39094,
39161,
39246,
39336,
39428,
39510,
39528,
39620,
39710,
39807,
39825,
39882,
39978,
40065,
40159,
40181,
40199,
40257,
40352,
40439,
40533,
40555,
40573,
40587,
40597,
40606,
40617,
40701,
40787,
40831,
40843,
40917,
40965,
41014,
41071,
41129,
41166,
41240,
41254,
41273,
41324,
41338,
41375,
41450,
41464,
41483,
41535,
41549,
41598,
41681,
41736,
41760,
41774,
41804,
41829,
41854,
41882,
41913,
41945,
41958,
42019,
42087,
42155,
42224,
42283,
42346,
42360,
42432,
42506,
42558,
42619,
42691,
42765,
42786,
42864,
42948,
42969,
43033,
43149,
43236,
43325,
43388,
43411,
43429,
43443,
43453,
43462,
43473,
43559,
43639,
43651,
43727,
43799,
43840,
43923,
43962,
43995,
44013,
44098,
44138,
44171,
44189,
44279,
44319,
44352,
44370,
44460,
44500,
44533,
44551,
44647,
44687,
44720,
44738,
44752,
44794,
44845,
44884,
44902,
44955,
44995,
45028,
45046,
45104,
45144,
45177,
45195,
45253,
45293,
45326,
45344,
45408,
45448,
45481,
45499,
45513,
45539,
45549,
45558,
45569,
45643,
45655,
45705,
45763,
45773,
45782,
45793,
45868,
45880,
45931,
45990,
46001,
46011,
46023,
46099,
46112,
46164,
46224,
46235,
46245,
46257,
46342,
46355,
46415,
46483,
46494,
46504,
46516,
46601,
46614,
46674,
46742,
46753,
46763,
46775,
46851,
46864,
46916,
46996,
47007,
47013,
47058,
47097,
47108,
47114,
47154,
47188,
47199,
47209,
47221,
47278,
47291,
47362,
47439,
47497,
47538,
47571,
47586,
47597,
47607,
47636,
47650,
47757,
47832,
47846,
47862,
47947,
48006,
48023,
48088,
48122,
48158,
48176,
48207,
48221,
48277,
48330,
48366,
48406,
48424,
48482,
48521,
48575,
48632,
48667,
48755,
48840,
48879,
48902,
48921,
48939,
48997,
49068,
49104,
49167,
49197,
49231,
49250,
49274,
49364,
49437,
49472,
49491,
49506,
49520,
49536,
49623,
49707,
49724,
49765,
49802,
49838,
49856,
49912,
49952,
50022,
50070,
50130,
50177,
50232,
50284,
50338,
50380,
50408,
50465,
50519,
50561,
50590,
50613,
50657,
50676,
50691,
50705,
50721,
50788,
50805,
50882,
50922,
50961,
50979,
51033,
51051,
51090,
51124,
51143,
51167,
51207,
51256,
51300,
51361,
51427,
51490,
51536,
51567,
51594,
51632,
51697,
51724,
51762,
51804,
51831,
51870,
51893,
51928,
51947,
51962,
51979,
51995,
52054,
52071,
52163,
52234,
52268,
52287,
52311,
52346,
52365,
52380,
52391,
52401,
52407
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 52407,
"ccnet_original_nlines": 1170,
"rps_doc_curly_bracket": 0.008319499902427197,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.13059571385383606,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.012030079960823059,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.5386928915977478,
"rps_doc_frac_unique_words": 0.4194011986255646,
"rps_doc_mean_word_length": 7.195448875427246,
"rps_doc_num_sentences": 645,
"rps_doc_symbol_to_word_ratio": 0.002082129940390587,
"rps_doc_unigram_entropy": 6.327409744262695,
"rps_doc_word_count": 4175,
"rps_doc_frac_chars_dupe_10grams": 0.0081555200740695,
"rps_doc_frac_chars_dupe_5grams": 0.1182384118437767,
"rps_doc_frac_chars_dupe_6grams": 0.08658166974782944,
"rps_doc_frac_chars_dupe_7grams": 0.048766691237688065,
"rps_doc_frac_chars_dupe_8grams": 0.01967311091721058,
"rps_doc_frac_chars_dupe_9grams": 0.018474750220775604,
"rps_doc_frac_chars_top_2gram": 0.008588260039687157,
"rps_doc_frac_chars_top_3gram": 0.005126330070197582,
"rps_doc_frac_chars_top_4gram": 0.010186079889535904,
"rps_doc_books_importance": -4444.015625,
"rps_doc_books_importance_length_correction": -4444.015625,
"rps_doc_openwebtext_importance": -2613.4140625,
"rps_doc_openwebtext_importance_length_correction": -2613.4140625,
"rps_doc_wikipedia_importance": -2037.3533935546875,
"rps_doc_wikipedia_importance_length_correction": -2037.3533935546875
},
"fasttext": {
"dclm": 0.9952414631843567,
"english": 0.20517346262931824,
"fineweb_edu_approx": 1.9772552251815796,
"eai_general_math": 0.7615935206413269,
"eai_open_web_math": 0.32010483741760254,
"eai_web_code": 0.927588939666748
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "511.3",
"labels": {
"level_1": "Science and Natural history",
"level_2": "Mathematics",
"level_3": "Arithmetic"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "4",
"label": "Analyze"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "4",
"label": "Code/Software"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "0",
"label": "No missing content"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "3",
"label": "Academic Writing"
}
},
"reasoning_depth": {
"primary": {
"code": "4",
"label": "Advanced Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "4",
"label": "Graduate/Expert Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
3,078,744,342,664,522,000
|
Parenthesis Checker
Submissions: 86558 Accuracy:
27.18%
Difficulty: Medium Marks: 4
Given an expression string exp. Examine whether the pairs and the orders of “{“,”}”,”(“,”)”,”[“,”]” are correct in exp.
For example, the program should print 'balanced' for exp = “[()]{}{[()()]()}” and 'not balanced' for exp = “[(])”
Input:
The first line of input contains an integer T denoting the number of test cases. Each test case consists of a string of expression, in a separate line.
Output:
Print 'balanced' without quotes if the pair of parenthesis is balanced else print 'not balanced' in a separate line.
Constraints:
1 ≤ T ≤ 100
1 ≤ |s| ≤ 105
Example:
Input:
3
{([])}
()
([]
Output:
balanced
balanced
not balanced
** For More Input/Output Examples Use 'Expected Output' option **
Author: shef5
If you have purchased any course from GeeksforGeeks then please ask your doubt on course discussion forum. You will get quick replies from GFG Moderators there.
Need help with your code? Please use ide.geeksforgeeks.org, generate link and share the link here.
to report an issue on this page.
|
{
"url": "https://practice.geeksforgeeks.org/problems/parenthesis-checker/0",
"source_domain": "practice.geeksforgeeks.org",
"snapshot_id": "crawl=CC-MAIN-2019-26",
"warc_metadata": {
"Content-Length": "97960",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:QKUWJMFXCI42FGJ4VZN56RZKD6O3THQZ",
"WARC-Concurrent-To": "<urn:uuid:fc5a94d4-61c2-4d99-827a-416656d81e70>",
"WARC-Date": "2019-06-25T05:43:32Z",
"WARC-IP-Address": "34.212.79.80",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:5QSVGFPAV37VJCF72HLW74TGAAOG2IDB",
"WARC-Record-ID": "<urn:uuid:8e581747-2c88-432d-a022-4f9072407118>",
"WARC-Target-URI": "https://practice.geeksforgeeks.org/problems/parenthesis-checker/0",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:49ad95a1-57ff-4e53-8a3e-334facedd554>"
},
"warc_info": "isPartOf: CC-MAIN-2019-26\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for June 2019\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-154-230-119.ec2.internal\r\nsoftware: Apache Nutch 1.15 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.1-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
20,
51,
52,
59,
60,
92,
93,
213,
327,
328,
335,
488,
489,
497,
614,
615,
628,
640,
654,
655,
664,
671,
672,
674,
681,
684,
688,
689,
697,
706,
715,
728,
729,
795,
796,
810,
811,
812,
973,
974,
975,
976,
1075,
1076
],
"line_end_idx": [
20,
51,
52,
59,
60,
92,
93,
213,
327,
328,
335,
488,
489,
497,
614,
615,
628,
640,
654,
655,
664,
671,
672,
674,
681,
684,
688,
689,
697,
706,
715,
728,
729,
795,
796,
810,
811,
812,
973,
974,
975,
976,
1075,
1076,
1108
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 1108,
"ccnet_original_nlines": 44,
"rps_doc_curly_bracket": 0.007220219820737839,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.28378379344940186,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.01351351011544466,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.28828829526901245,
"rps_doc_frac_unique_words": 0.6294117569923401,
"rps_doc_mean_word_length": 4.8176469802856445,
"rps_doc_num_sentences": 13,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.475452423095703,
"rps_doc_word_count": 170,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.04029304161667824,
"rps_doc_frac_chars_top_3gram": 0.034188028424978256,
"rps_doc_frac_chars_top_4gram": 0.03907204046845436,
"rps_doc_books_importance": -109.60565185546875,
"rps_doc_books_importance_length_correction": -109.60565185546875,
"rps_doc_openwebtext_importance": -60.659854888916016,
"rps_doc_openwebtext_importance_length_correction": -52.65422058105469,
"rps_doc_wikipedia_importance": -51.76325607299805,
"rps_doc_wikipedia_importance_length_correction": -51.76325607299805
},
"fasttext": {
"dclm": 0.06524592638015747,
"english": 0.7565879225730896,
"fineweb_edu_approx": 1.460986614227295,
"eai_general_math": 0.5811555981636047,
"eai_open_web_math": 0.03907895088195801,
"eai_web_code": 0.06650341302156448
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "-1",
"labels": {
"level_1": "",
"level_2": "",
"level_3": ""
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "4",
"label": "Code/Software"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "23",
"label": "Tutorial"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-7,861,514,123,199,365,000
|
cancel
Showing results for
Search instead for
Did you mean:
cancel
146
Views
0
Helpful
2
Replies
Beginner
VPN o365 MFA authntictaion with Cisco ISE
Dear All,
Looking for help for the below scenario.
We have a Cisco ISE setup to authenticate VPN users and trying to do compliance check with Posture assessment. Based on the posture status VPN user will receive an authorization profile. We also want to do the o365 MFA for VPN users.
1. Is it supported by Cisco ISE? if yes how can we achieve the same?
2. Is my understanding correct on , Cisco ISE will not check the posture until the radius session is being maintained on ISE. Means without sending the authentication request to ISE, posture, and Enforcement is not possible?
3. What is the best way to achieve the MFA with ISE for VPN users/
Thanks a lot in Advance.
Regards,
MD
2 REPLIES 2
Highlighted
VIP Advisor
Re: VPN o365 MFA authntictaion with Cisco ISE
personally, suggest the below method :
https://community.cisco.com/t5/security-documents/how-to-deploy-ise-device-admin-with-duo-mfa/ta-p/3821231
BB
*** Rate All Helpful Responses ***
Cisco Employee
Re: VPN o365 MFA authntictaion with Cisco ISE
1 & 3: I would suggest to configure it for SAML auth with the ASA as the SP. See AnyConnect: Azure AD SAML SSO - Cisco Community and then configure ASA to perform authorize-only to ISE
If using RADIUS, Azure is no longer supporting on-prem MFA server so you would need NPS. Deploy cloud-based MFA
2: You are correct on this.
|
{
"url": "https://community.cisco.com/t5/policy-and-access/vpn-o365-mfa-authntictaion-with-cisco-ise/m-p/3955526",
"source_domain": "community.cisco.com",
"snapshot_id": "crawl=CC-MAIN-2019-47",
"warc_metadata": {
"Content-Length": "174456",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:JMZW6V6ZRNLA52AEQY6OHUET47QX3HNK",
"WARC-Concurrent-To": "<urn:uuid:5007c48f-64cf-4673-a9ef-d9864f36956d>",
"WARC-Date": "2019-11-15T20:24:04Z",
"WARC-IP-Address": "208.74.205.244",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:FJHBP7JAKOW4W4EVYAA54FA5SYOJ63OQ",
"WARC-Record-ID": "<urn:uuid:b5828bdc-3fcf-4733-ad4d-a88b7697e8ee>",
"WARC-Target-URI": "https://community.cisco.com/t5/policy-and-access/vpn-o365-mfa-authntictaion-with-cisco-ise/m-p/3955526",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:72215bbe-5baf-42de-b4d7-34b0b616b78a>"
},
"warc_info": "isPartOf: CC-MAIN-2019-47\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for November 2019\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-221.ec2.internal\r\nsoftware: Apache Nutch 1.16 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.1-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
7,
28,
48,
63,
70,
74,
80,
82,
90,
92,
100,
109,
110,
152,
153,
163,
164,
166,
167,
209,
210,
212,
213,
449,
450,
452,
453,
522,
523,
748,
749,
816,
817,
819,
820,
845,
846,
848,
849,
858,
859,
862,
863,
865,
866,
878,
890,
902,
903,
949,
950,
989,
990,
992,
993,
1100,
1101,
1104,
1139,
1154,
1155,
1201,
1202,
1387,
1388,
1501,
1502
],
"line_end_idx": [
7,
28,
48,
63,
70,
74,
80,
82,
90,
92,
100,
109,
110,
152,
153,
163,
164,
166,
167,
209,
210,
212,
213,
449,
450,
452,
453,
522,
523,
748,
749,
816,
817,
819,
820,
845,
846,
848,
849,
858,
859,
862,
863,
865,
866,
878,
890,
902,
903,
949,
950,
989,
990,
992,
993,
1100,
1101,
1104,
1139,
1154,
1155,
1201,
1202,
1387,
1388,
1501,
1502,
1529
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 1529,
"ccnet_original_nlines": 67,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3072100281715393,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.11912225931882858,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.21003134548664093,
"rps_doc_frac_unique_words": 0.5514403581619263,
"rps_doc_mean_word_length": 4.827160358428955,
"rps_doc_num_sentences": 17,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.575719833374023,
"rps_doc_word_count": 243,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.09292413294315338,
"rps_doc_frac_chars_dupe_6grams": 0.09292413294315338,
"rps_doc_frac_chars_dupe_7grams": 0.09292413294315338,
"rps_doc_frac_chars_dupe_8grams": 0.06308609992265701,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.040920719504356384,
"rps_doc_frac_chars_top_3gram": 0.02557544969022274,
"rps_doc_frac_chars_top_4gram": 0.05882352963089943,
"rps_doc_books_importance": -136.60658264160156,
"rps_doc_books_importance_length_correction": -125.64080047607422,
"rps_doc_openwebtext_importance": -84.84345245361328,
"rps_doc_openwebtext_importance_length_correction": -84.84345245361328,
"rps_doc_wikipedia_importance": -70.39154052734375,
"rps_doc_wikipedia_importance_length_correction": -57.33919906616211
},
"fasttext": {
"dclm": 0.02521347999572754,
"english": 0.8373221755027771,
"fineweb_edu_approx": 1.061401128768921,
"eai_general_math": 0.005336170084774494,
"eai_open_web_math": 0.273584246635437,
"eai_web_code": 0.00002538999979151413
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.822",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.67",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "2",
"label": "Click Here References"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "21",
"label": "Customer Support"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "4",
"label": "Graduate/Expert Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-417,161,559,170,168,000
|
~fitzsim/grub
Add KBoot/GRUB glue code
Port memory_alloc, device_read, and fs_read to GRUB.
Port mezzano_locate_image to GRUB
As part of this port, support loading from a .image file or from a raw
device. Check at the start of the byte range, and also just after the
KBoot partitions. This allows loading an MBuild-produced .image
directly.
Remove some unused KBoot code
Port config_cmd_mezzano to grub_cmd_mezzano
Improve verbose message output
Flush output to the terminal on every mprintf invocation. Work around a
GRUB compilation error due to the use of %. Comment on implication of
retrieving the framebuffer pointer from GRUB.
Port adding pages to buddy allocator
Port KBoot-specific memory region traversal logic to GRUB.
Make some format strings GRUB-compatible
GRUB does not implement some of the format string extensions that KBoot
provides. Simplify format strings that used these extensions.
Mark some parameters unused
Elimiate some compiler warnings.
Adjust mezzano_arch_enter_real calling conventions
Change mezzano_arch_enter_real's implementation to match where the
calling GRUB function places arguments.
Also load the global descriptor table.
Focus transition page table mappings
The GRUB Mezzano module does not know its own extents in memory.
Therefore only map the regions that are required in the transition page
table rather than attempting to map the whole module.
Rename __ASM__ preprocessor macro to ASM_FILE
KBoot uses __ASM__ where GRUB uses ASM_FILE.
Remove inclusions of unused KBoot headers
Remove some unneeded KBoot code
Remove code that causes build failures due to external references.
mezzano: Import files from KBoot
Import unmodified files from https://github.com/froggey/kboot.git
revision 92b9833fe69fe595e2e8ba42f60cfa63e8a30ce3.
Ignore docs/grub.info-1 and docs/grub.info-2
Hack around some build failures
Next
|
{
"url": "https://git.sr.ht/~fitzsim/grub/log",
"source_domain": "git.sr.ht",
"snapshot_id": "CC-MAIN-2023-40",
"warc_metadata": {
"Content-Length": "17683",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:CQBBYZIS6JXJEDOH7JWXLVZDNLQJPVRB",
"WARC-Concurrent-To": "<urn:uuid:7fb68aa0-dc32-4371-94fa-a0571ca12c6a>",
"WARC-Date": "2023-09-24T06:40:40Z",
"WARC-IP-Address": "173.195.146.142",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:KA7OWOY4Y2AMBV76XDKQQGYWCG22LZCX",
"WARC-Record-ID": "<urn:uuid:61449270-7623-450b-a23a-5b3bf814ea92>",
"WARC-Target-URI": "https://git.sr.ht/~fitzsim/grub/log",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:0fe0d124-c92e-4e3c-931c-69d7b9c050a7>"
},
"warc_info": "isPartOf: CC-MAIN-2023-40\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for September/October 2023\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-5\r\nsoftware: Apache Nutch 1.19 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.5-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
14,
15,
40,
41,
94,
128,
129,
200,
271,
336,
346,
376,
420,
451,
452,
525,
596,
642,
679,
680,
739,
780,
781,
853,
916,
944,
945,
978,
1029,
1030,
1097,
1137,
1138,
1177,
1214,
1215,
1280,
1352,
1406,
1452,
1453,
1498,
1540,
1572,
1573,
1640,
1673,
1674,
1740,
1791,
1836,
1868
],
"line_end_idx": [
14,
15,
40,
41,
94,
128,
129,
200,
271,
336,
346,
376,
420,
451,
452,
525,
596,
642,
679,
680,
739,
780,
781,
853,
916,
944,
945,
978,
1029,
1030,
1097,
1137,
1138,
1177,
1214,
1215,
1280,
1352,
1406,
1452,
1453,
1498,
1540,
1572,
1573,
1640,
1673,
1674,
1740,
1791,
1836,
1868,
1872
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 1872,
"ccnet_original_nlines": 52,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.27812498807907104,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.046875,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.140625,
"rps_doc_frac_unique_words": 0.6038461327552795,
"rps_doc_mean_word_length": 5.857692241668701,
"rps_doc_num_sentences": 25,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.759842395782471,
"rps_doc_word_count": 260,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.01181877963244915,
"rps_doc_frac_chars_top_3gram": 0.02495075948536396,
"rps_doc_frac_chars_top_4gram": 0,
"rps_doc_books_importance": -142.78494262695312,
"rps_doc_books_importance_length_correction": -142.77024841308594,
"rps_doc_openwebtext_importance": -85.82730865478516,
"rps_doc_openwebtext_importance_length_correction": -85.82730865478516,
"rps_doc_wikipedia_importance": -58.3133430480957,
"rps_doc_wikipedia_importance_length_correction": -58.31333541870117
},
"fasttext": {
"dclm": 0.03696250915527344,
"english": 0.6848132014274597,
"fineweb_edu_approx": 2.654733180999756,
"eai_general_math": 0.6418055891990662,
"eai_open_web_math": 0.17957162857055664,
"eai_web_code": 0.8802481889724731
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.4",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.02",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "4",
"label": "Analyze"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "4",
"label": "Code/Software"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "6",
"label": "Content Listing"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "6",
"label": "Not Applicable/Indeterminate"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "4",
"label": "Graduate/Expert Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-181,425,082,413,604,400
|
utf8
This is a discussion on utf8 within the C++ Programming forums, part of the General Programming Boards category; Hi CBoard members. I want to write a function which will return true or false based on if the given ...
1. #1
Registered User
Join Date
Jun 2008
Posts
1
utf8
Hi CBoard members.
I want to write a function which will return true or false based on if the given string is Utf8 encoded or not.
for example:
Code:
boo isUtf8(const string & str) {}
Since this is a multi byte encoding, currently I am just checking null chars. If there are more than one null chars then the string is Utf8 encoded else just a plain ASCII string.
Please tell me what else can I check for in my function?
2. #2
Cat without Hat CornedBee's Avatar
Join Date
Apr 2003
Posts
8,892
The null char check won't work. UTF-8 doesn't contain NULs.
There is no definite way of checking for UTF-8. There are some leads.
1) If the first three bytes are 0xEF 0xBB 0xBF, you've probably found a UTF-8-encoded byte order mark. Probability of UTF-8 is very high. But UTF-8 doesn't require the BOM, some editors don't understand it, and to the best of my knowledge, Notepad is the only editor that inserts it.
2) If you don't have a BOM, parse the whole file, or at least a part of it (the more, the better the results, but of course it takes longer). If you find only bytes in the 0x7F range, the text is probably ASCII, so you can treat it as UTF-8. If you find high-bit bytes, check them for UTF-8 validity. If the sequences are invalid, you don't have UTF-8. If all sequences are valid, you probably have UTF-8.
All the buzzt!
CornedBee
"There is not now, nor has there ever been, nor will there ever be, any programming language in which it is the least bit difficult to write bad code."
- Flon's Law
Popular pages Recent additions subscribe to a feed
Similar Threads
1. tolower and locale
By MK27 in forum C Programming
Replies: 16
Last Post: 02-03-2009, 08:05 PM
2. adjusting character counts for utf8
By MK27 in forum C Programming
Replies: 32
Last Post: 02-03-2009, 06:07 PM
3. utf8 en-de coding
By SurferIX in forum C Programming
Replies: 4
Last Post: 05-18-2008, 05:23 PM
4. How to convert raw text with accent to UTF8.
By intmail in forum Linux Programming
Replies: 1
Last Post: 08-09-2006, 10:47 AM
5. File Reading and storing to 1 variable
By Rare177 in forum C Programming
Replies: 34
Last Post: 07-13-2004, 12:58 PM
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21
|
{
"url": "http://cboard.cprogramming.com/cplusplus-programming/104216-utf8.html",
"source_domain": "cboard.cprogramming.com",
"snapshot_id": "crawl=CC-MAIN-2014-15",
"warc_metadata": {
"Content-Length": "42443",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:SQXZVC2ZNL2PCCGOGWU4UQQDRC5YXCWO",
"WARC-Concurrent-To": "<urn:uuid:7c44c867-ea3a-4e3c-91c7-b9f1edf30870>",
"WARC-Date": "2014-04-17T19:13:50Z",
"WARC-IP-Address": "76.74.254.184",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:EEP6TLBSNCAEJXBA2SMZJ2XFWTOPJBKD",
"WARC-Record-ID": "<urn:uuid:b88a6e2f-db59-4588-b86c-f35a2c59ad16>",
"WARC-Target-URI": "http://cboard.cprogramming.com/cplusplus-programming/104216-utf8.html",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:d804cb30-38cd-4b8b-8297-a147ef790107>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-147-4-33.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2014-15\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web with URLs provided by Blekko for April 2014\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
5,
6,
223,
224,
232,
252,
266,
279,
289,
295,
296,
305,
306,
329,
445,
446,
463,
473,
511,
695,
696,
757,
758,
766,
805,
819,
832,
842,
852,
916,
917,
991,
1279,
1689,
1708,
1722,
1723,
1879,
1896,
1897,
1948,
1949,
1965,
1966,
1990,
2025,
2041,
2077,
2118,
2153,
2169,
2205,
2228,
2267,
2282,
2318,
2368,
2410,
2425,
2461,
2505,
2543,
2559,
2595,
2596
],
"line_end_idx": [
5,
6,
223,
224,
232,
252,
266,
279,
289,
295,
296,
305,
306,
329,
445,
446,
463,
473,
511,
695,
696,
757,
758,
766,
805,
819,
832,
842,
852,
916,
917,
991,
1279,
1689,
1708,
1722,
1723,
1879,
1896,
1897,
1948,
1949,
1965,
1966,
1990,
2025,
2041,
2077,
2118,
2153,
2169,
2205,
2228,
2267,
2282,
2318,
2368,
2410,
2425,
2461,
2505,
2543,
2559,
2595,
2596,
2649
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 2649,
"ccnet_original_nlines": 65,
"rps_doc_curly_bracket": 0.000754999986384064,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.29228243231773376,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.049261078238487244,
"rps_doc_frac_lines_end_with_ellipsis": 0.015151520259678364,
"rps_doc_frac_no_alph_words": 0.3136289119720459,
"rps_doc_frac_unique_words": 0.5076586604118347,
"rps_doc_mean_word_length": 4.109409332275391,
"rps_doc_num_sentences": 30,
"rps_doc_symbol_to_word_ratio": 0.004926110152155161,
"rps_doc_unigram_entropy": 5.091290473937988,
"rps_doc_word_count": 457,
"rps_doc_frac_chars_dupe_10grams": 0.08413206040859222,
"rps_doc_frac_chars_dupe_5grams": 0.14589989185333252,
"rps_doc_frac_chars_dupe_6grams": 0.11821085959672928,
"rps_doc_frac_chars_dupe_7grams": 0.11821085959672928,
"rps_doc_frac_chars_dupe_8grams": 0.08413206040859222,
"rps_doc_frac_chars_dupe_9grams": 0.08413206040859222,
"rps_doc_frac_chars_top_2gram": 0.03194887936115265,
"rps_doc_frac_chars_top_3gram": 0.017039399594068527,
"rps_doc_frac_chars_top_4gram": 0.04046858102083206,
"rps_doc_books_importance": -249.46482849121094,
"rps_doc_books_importance_length_correction": -249.46482849121094,
"rps_doc_openwebtext_importance": -167.6222686767578,
"rps_doc_openwebtext_importance_length_correction": -167.6222686767578,
"rps_doc_wikipedia_importance": -117.93733215332031,
"rps_doc_wikipedia_importance_length_correction": -117.93733215332031
},
"fasttext": {
"dclm": 0.028882620856165886,
"english": 0.8695042133331299,
"fineweb_edu_approx": 1.934924840927124,
"eai_general_math": 0.07020384073257446,
"eai_open_web_math": 0.16719818115234375,
"eai_web_code": 0.00032531999750062823
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.432",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-6,435,030,667,980,657,000
|
/[baselayout]/trunk/src/rc.c
Gentoo
Contents of /trunk/src/rc.c
Parent Directory Parent Directory | Revision Log Revision Log
Revision 2700 - (show annotations) (download) (as text)
Mon May 14 12:48:37 2007 UTC (10 years ago) by uberlord
File MIME type: text/x-csrc
File size: 34873 byte(s)
RC_INTERACTIVE now works, #178331.
1 /*
2 rc.c
3 rc - manager for init scripts which control the startup, shutdown
4 and the running of daemons on a Gentoo system.
5
6 Also a multicall binary for various commands that can be used in shell
7 scripts to query service state, mark service state and provide the
8 Gentoo einfo family of informational functions.
9
10 Copyright 2007 Gentoo Foundation
11 Released under the GPLv2
12 */
13
14 #include <sys/types.h>
15 #include <sys/stat.h>
16 #include <sys/utsname.h>
17 #include <sys/wait.h>
18 #include <errno.h>
19 #include <ctype.h>
20 #include <libgen.h>
21 #include <limits.h>
22 #include <stdbool.h>
23 #include <stdio.h>
24 #include <stdlib.h>
25 #include <signal.h>
26 #include <string.h>
27 #include <termios.h>
28 #include <unistd.h>
29
30 #include "einfo.h"
31 #include "rc.h"
32 #include "rc-misc.h"
33 #include "rc-plugin.h"
34 #include "strlist.h"
35
36 #define INITSH RC_LIBDIR "sh/init.sh"
37 #define INITEARLYSH RC_LIBDIR "sh/init-early.sh"
38 #define HALTSH RC_INITDIR "halt.sh"
39 #define SULOGIN "/sbin/sulogin"
40
41 #define RC_SVCDIR_STARTING RC_SVCDIR "starting/"
42 #define RC_SVCDIR_INACTIVE RC_SVCDIR "inactive/"
43 #define RC_SVCDIR_STARTED RC_SVCDIR "started/"
44 #define RC_SVCDIR_COLDPLUGGED RC_SVCDIR "coldplugged/"
45
46 #define INTERACTIVE RC_SVCDIR "interactive"
47
48 #define DEVBOOT "/dev/.rcboot"
49
50 /* Cleanup anything in main */
51 #define CHAR_FREE(_item) if (_item) { \
52 free (_item); \
53 _item = NULL; \
54 }
55
56 extern char **environ;
57
58 static char *applet = NULL;
59 static char **env = NULL;
60 static char **newenv = NULL;
61 static char **coldplugged_services = NULL;
62 static char **stop_services = NULL;
63 static char **start_services = NULL;
64 static rc_depinfo_t *deptree = NULL;
65 static char **types = NULL;
66 static char *tmp = NULL;
67
68 struct termios *termios_orig = NULL;
69
70 typedef struct pidlist
71 {
72 pid_t pid;
73 struct pidlist *next;
74 } pidlist_t;
75 static pidlist_t *service_pids = NULL;
76
77 static void cleanup (void)
78 {
79 pidlist_t *pl = service_pids;
80
81 rc_plugin_unload ();
82
83 if (termios_orig) {
84 tcsetattr (STDIN_FILENO, TCSANOW, termios_orig);
85 free (termios_orig);
86 }
87
88 while (pl) {
89 pidlist_t *p = pl->next;
90 free (pl);
91 pl = p;
92 }
93
94 rc_strlist_free (env);
95 rc_strlist_free (newenv);
96 rc_strlist_free (coldplugged_services);
97 rc_strlist_free (stop_services);
98 rc_strlist_free (start_services);
99 rc_free_deptree (deptree);
100 rc_strlist_free (types);
101
102 /* Clean runlevel start, stop markers */
103 if (rc_is_dir (RC_SVCDIR "softscripts.new"))
104 rc_rm_dir (RC_SVCDIR "softscripts.new", true);
105 if (rc_is_dir (RC_SVCDIR "softscripts.old"))
106 rc_rm_dir (RC_SVCDIR "softscripts.old", true);
107
108 free (applet);
109 }
110
111 static int do_e (int argc, char **argv)
112 {
113 int retval = EXIT_SUCCESS;
114 int i;
115 int l = 0;
116 char *message = NULL;
117 char *p;
118 char *fmt = NULL;
119
120 if (strcmp (applet, "eval_ecolors") == 0) {
121 printf ("GOOD='%s'\nWARN='%s'\nBAD='%s'\nHILITE='%s'\nBRACKET='%s'\nNORMAL='%s'\n",
122 ecolor (ecolor_good),
123 ecolor (ecolor_warn),
124 ecolor (ecolor_bad),
125 ecolor (ecolor_hilite),
126 ecolor (ecolor_bracket),
127 ecolor (ecolor_normal));
128 exit (EXIT_SUCCESS);
129 }
130
131 if (strcmp (applet, "eend") == 0 ||
132 strcmp (applet, "ewend") == 0 ||
133 strcmp (applet, "veend") == 0 ||
134 strcmp (applet, "vweend") == 0)
135 {
136 if (argc > 0) {
137 errno = 0;
138 retval = strtol (argv[0], NULL, 0);
139 if (errno != 0)
140 retval = EXIT_FAILURE;
141 else {
142 argc--;
143 argv++;
144 }
145 }
146 else
147 retval = EXIT_FAILURE;
148 }
149
150 if (argc > 0) {
151 for (i = 0; i < argc; i++)
152 l += strlen (argv[i]) + 1;
153
154 message = rc_xmalloc (l);
155 p = message;
156
157 for (i = 0; i < argc; i++) {
158 if (i > 0)
159 *p++ = ' ';
160 memcpy (p, argv[i], strlen (argv[i]));
161 p += strlen (argv[i]);
162 }
163 *p = 0;
164 }
165
166 if (message)
167 fmt = rc_xstrdup ("%s");
168
169 if (strcmp (applet, "einfo") == 0)
170 einfo (fmt, message);
171 else if (strcmp (applet, "einfon") == 0)
172 einfon (fmt, message);
173 else if (strcmp (applet, "ewarn") == 0)
174 ewarn (fmt, message);
175 else if (strcmp (applet, "ewarnn") == 0)
176 ewarnn (fmt, message);
177 else if (strcmp (applet, "eerror") == 0) {
178 eerror (fmt, message);
179 retval = 1;
180 } else if (strcmp (applet, "eerrorn") == 0) {
181 eerrorn (fmt, message);
182 retval = 1;
183 } else if (strcmp (applet, "ebegin") == 0)
184 ebegin (fmt, message);
185 else if (strcmp (applet, "eend") == 0)
186 eend (retval, fmt, message);
187 else if (strcmp (applet, "ewend") == 0)
188 ewend (retval, fmt, message);
189 else if (strcmp (applet, "veinfo") == 0)
190 einfov (fmt, message);
191 else if (strcmp (applet, "veinfon") == 0)
192 einfovn (fmt, message);
193 else if (strcmp (applet, "vewarn") == 0)
194 ewarnv (fmt, message);
195 else if (strcmp (applet, "vewarnn") == 0)
196 ewarnvn (fmt, message);
197 else if (strcmp (applet, "vebegin") == 0)
198 ebeginv (fmt, message);
199 else if (strcmp (applet, "veend") == 0)
200 eendv (retval, fmt, message);
201 else if (strcmp (applet, "vewend") == 0)
202 ewendv (retval, fmt, message);
203 else if (strcmp (applet, "eindent") == 0)
204 eindent ();
205 else if (strcmp (applet, "eoutdent") == 0)
206 eoutdent ();
207 else if (strcmp (applet, "veindent") == 0)
208 eindentv ();
209 else if (strcmp (applet, "veoutdent") == 0)
210 eoutdentv ();
211 else if (strcmp (applet, "eflush") == 0)
212 eflush ();
213 else {
214 eerror ("%s: unknown applet", applet);
215 retval = EXIT_FAILURE;
216 }
217
218 if (fmt)
219 free (fmt);
220 if (message)
221 free (message);
222 return (retval);
223 }
224
225 static int do_service (int argc, char **argv)
226 {
227 bool ok = false;
228
229 if (argc < 1 || ! argv[0] || strlen (argv[0]) == 0)
230 eerrorx ("%s: no service specified", applet);
231
232 if (strcmp (applet, "service_started") == 0)
233 ok = rc_service_state (argv[0], rc_service_started);
234 else if (strcmp (applet, "service_stopped") == 0)
235 ok = rc_service_state (argv[0], rc_service_stopped);
236 else if (strcmp (applet, "service_inactive") == 0)
237 ok = rc_service_state (argv[0], rc_service_inactive);
238 else if (strcmp (applet, "service_starting") == 0)
239 ok = rc_service_state (argv[0], rc_service_starting);
240 else if (strcmp (applet, "service_stopping") == 0)
241 ok = rc_service_state (argv[0], rc_service_stopping);
242 else if (strcmp (applet, "service_coldplugged") == 0)
243 ok = rc_service_state (argv[0], rc_service_coldplugged);
244 else if (strcmp (applet, "service_wasinactive") == 0)
245 ok = rc_service_state (argv[0], rc_service_wasinactive);
246 else if (strcmp (applet, "service_started_daemon") == 0) {
247 int idx = 0;
248 if (argc > 2)
249 sscanf (argv[2], "%d", &idx);
250 exit (rc_service_started_daemon (argv[0], argv[1], idx)
251 ? 0 : 1);
252 } else
253 eerrorx ("%s: unknown applet", applet);
254
255 return (ok ? EXIT_SUCCESS : EXIT_FAILURE);
256 }
257
258 static int do_mark_service (int argc, char **argv)
259 {
260 bool ok = false;
261 char *svcname = getenv ("SVCNAME");
262
263 if (argc < 1 || ! argv[0] || strlen (argv[0]) == 0)
264 eerrorx ("%s: no service specified", applet);
265
266 if (strcmp (applet, "mark_service_started") == 0)
267 ok = rc_mark_service (argv[0], rc_service_started);
268 else if (strcmp (applet, "mark_service_stopped") == 0)
269 ok = rc_mark_service (argv[0], rc_service_stopped);
270 else if (strcmp (applet, "mark_service_inactive") == 0)
271 ok = rc_mark_service (argv[0], rc_service_inactive);
272 else if (strcmp (applet, "mark_service_starting") == 0)
273 ok = rc_mark_service (argv[0], rc_service_starting);
274 else if (strcmp (applet, "mark_service_stopping") == 0)
275 ok = rc_mark_service (argv[0], rc_service_stopping);
276 else if (strcmp (applet, "mark_service_coldplugged") == 0)
277 ok = rc_mark_service (argv[0], rc_service_coldplugged);
278 else
279 eerrorx ("%s: unknown applet", applet);
280
281 /* If we're marking ourselves then we need to inform our parent runscript
282 process so they do not mark us based on our exit code */
283 if (ok && svcname && strcmp (svcname, argv[0]) == 0) {
284 char *runscript_pid = getenv ("RC_RUNSCRIPT_PID");
285 char *mtime;
286 pid_t pid = 0;
287 int l;
288
289 if (runscript_pid && sscanf (runscript_pid, "%d", &pid) == 1)
290 if (kill (pid, SIGHUP) != 0)
291 eerror ("%s: failed to signal parent %d: %s",
292 applet, pid, strerror (errno));
293
294 /* Remove the exclsive time test. This ensures that it's not
295 in control as well */
296 l = strlen (RC_SVCDIR "exclusive") +
297 strlen (svcname) +
298 strlen (runscript_pid) +
299 4;
300 mtime = rc_xmalloc (l);
301 snprintf (mtime, l, RC_SVCDIR "exclusive/%s.%s",
302 svcname, runscript_pid);
303 if (rc_exists (mtime) && unlink (mtime) != 0)
304 eerror ("%s: unlink: %s", applet, strerror (errno));
305 free (mtime);
306 }
307
308 return (ok ? EXIT_SUCCESS : EXIT_FAILURE);
309 }
310
311 static int do_options (int argc, char **argv)
312 {
313 bool ok = false;
314 char *service = getenv ("SVCNAME");
315
316 if (! service)
317 eerrorx ("%s: no service specified", applet);
318
319 if (argc < 1 || ! argv[0] || strlen (argv[0]) == 0)
320 eerrorx ("%s: no option specified", applet);
321
322 if (strcmp (applet, "get_options") == 0) {
323 char buffer[1024];
324 memset (buffer, 0, 1024);
325 ok = rc_get_service_option (service, argv[0], buffer);
326 if (ok)
327 printf ("%s", buffer);
328 } else if (strcmp (applet, "save_options") == 0)
329 ok = rc_set_service_option (service, argv[0], argv[1]);
330 else
331 eerrorx ("%s: unknown applet", applet);
332
333 return (ok ? EXIT_SUCCESS : EXIT_FAILURE);
334 }
335
336 static char read_key (bool block)
337 {
338 struct termios termios;
339 char c = 0;
340
341 if (! isatty (STDIN_FILENO))
342 return (false);
343
344 /* Now save our terminal settings. We need to restore them at exit as we
345 will be changing it for non-blocking reads for Interactive */
346 if (! termios_orig) {
347 termios_orig = rc_xmalloc (sizeof (struct termios));
348 tcgetattr (STDIN_FILENO, termios_orig);
349 }
350
351 tcgetattr (STDIN_FILENO, &termios);
352 termios.c_lflag &= ~(ICANON | ECHO);
353 if (block)
354 termios.c_cc[VMIN] = 1;
355 else {
356 termios.c_cc[VMIN] = 0;
357 termios.c_cc[VTIME] = 0;
358 }
359 tcsetattr (STDIN_FILENO, TCSANOW, &termios);
360
361 read (STDIN_FILENO, &c, 1);
362
363 tcsetattr (STDIN_FILENO, TCSANOW, termios_orig);
364
365 return (c);
366 }
367
368 static bool want_interactive (void)
369 {
370 char c;
371
372 if (! rc_is_env ("RC_INTERACTIVE", "yes"))
373 return (false);
374
375 c = read_key (false);
376 return ((c == 'I' || c == 'i') ? true : false);
377 }
378
379 static void mark_interactive (void)
380 {
381 FILE *fp = fopen (INTERACTIVE, "w");
382 if (fp)
383 fclose (fp);
384 }
385
386 static void sulogin (bool cont)
387 {
388 #ifdef __linux__
389 char *e = getenv ("RC_SYS");
390
391 /* VPS systems cannot do an sulogin */
392 if (e && strcmp (e, "VPS") == 0) {
393 execl ("/sbin/halt", "/sbin/halt", "-f", (char *) NULL);
394 eerrorx ("%s: unable to exec `/sbin/halt': %s", applet, strerror (errno));
395 }
396 #endif
397
398 newenv = rc_filter_env ();
399
400 if (cont) {
401 int status = 0;
402 #ifdef __linux__
403 char *tty = ttyname (fileno (stdout));
404 #endif
405
406 pid_t pid = vfork ();
407
408 if (pid == -1)
409 eerrorx ("%s: vfork: %s", applet, strerror (errno));
410 if (pid == 0) {
411 #ifdef __linux__
412 if (tty)
413 execle (SULOGIN, SULOGIN, tty, (char *) NULL, newenv);
414 else
415 execle (SULOGIN, SULOGIN, (char *) NULL, newenv);
416
417 eerror ("%s: unable to exec `%s': %s", applet, SULOGIN,
418 strerror (errno));
419 #else
420 execle ("/bin/sh", "/bin/sh", (char *) NULL, newenv);
421 eerror ("%s: unable to exec `/bin/sh': %s", applet,
422 strerror (errno));
423 #endif
424 _exit (EXIT_FAILURE);
425 }
426 waitpid (pid, &status, 0);
427 } else {
428 #ifdef __linux
429 execle ("/sbin/sulogin", "/sbin/sulogin", (char *) NULL, newenv);
430 eerrorx ("%s: unable to exec `/sbin/sulogin': %s", applet, strerror (errno));
431 #else
432 exit (EXIT_SUCCESS);
433 #endif
434 }
435 }
436
437 static void single_user (void)
438 {
439 #ifdef __linux__
440 execl ("/sbin/telinit", "/sbin/telinit", "S", (char *) NULL);
441 eerrorx ("%s: unable to exec `/sbin/telinit': %s",
442 applet, strerror (errno));
443 #else
444 if (kill (1, SIGTERM) != 0)
445 eerrorx ("%s: unable to send SIGTERM to init (pid 1): %s",
446 applet, strerror (errno));
447 exit (EXIT_SUCCESS);
448 #endif
449 }
450
451 static void set_ksoftlevel (const char *runlevel)
452 {
453 FILE *fp;
454
455 if (! runlevel ||
456 strcmp (runlevel, RC_LEVEL_BOOT) == 0 ||
457 strcmp (runlevel, RC_LEVEL_SINGLE) == 0 ||
458 strcmp (runlevel, RC_LEVEL_SYSINIT) == 0)
459 {
460 if (rc_exists (RC_SVCDIR "ksoftlevel") &&
461 unlink (RC_SVCDIR "ksoftlevel") != 0)
462 eerror ("unlink `%s': %s", RC_SVCDIR "ksoftlevel", strerror (errno));
463 return;
464 }
465
466 if (! (fp = fopen (RC_SVCDIR "ksoftlevel", "w"))) {
467 eerror ("fopen `%s': %s", RC_SVCDIR "ksoftlevel", strerror (errno));
468 return;
469 }
470
471 fprintf (fp, "%s", runlevel);
472 fclose (fp);
473 }
474
475 static void wait_for_services ()
476 {
477 int status = 0;
478 while (wait (&status) != -1);
479 }
480
481 static void add_pid (pid_t pid)
482 {
483 pidlist_t *sp = service_pids;
484 if (sp) {
485 while (sp->next)
486 sp = sp->next;
487 sp->next = rc_xmalloc (sizeof (pidlist_t));
488 sp = sp->next;
489 } else
490 sp = service_pids = rc_xmalloc (sizeof (pidlist_t));
491 memset (sp, 0, sizeof (pidlist_t));
492 sp->pid = pid;
493 }
494
495 static void remove_pid (pid_t pid)
496 {
497 pidlist_t *last = NULL;
498 pidlist_t *pl;
499
500 for (pl = service_pids; pl; pl = pl->next) {
501 if (pl->pid == pid) {
502 if (last)
503 last->next = pl->next;
504 else
505 service_pids = pl->next;
506 free (pl);
507 break;
508 }
509 last = pl;
510 }
511 }
512
513 static void handle_signal (int sig)
514 {
515 int serrno = errno;
516 char signame[10] = { '\0' };
517 char *run;
518 char *prev;
519 pidlist_t *pl;
520 pid_t pid;
521 int status = 0;
522
523 switch (sig) {
524 case SIGCHLD:
525 do {
526 pid = waitpid (-1, &status, WNOHANG);
527 if (pid < 0) {
528 if (errno != ECHILD)
529 eerror ("waitpid: %s", strerror (errno));
530 return;
531 }
532 } while (! WIFEXITED (status) && ! WIFSIGNALED (status));
533
534 /* Remove that pid from our list */
535 if (pid > 0)
536 remove_pid (pid);
537 break;
538
539 case SIGINT:
540 if (! signame[0])
541 snprintf (signame, sizeof (signame), "SIGINT");
542 case SIGTERM:
543 if (! signame[0])
544 snprintf (signame, sizeof (signame), "SIGTERM");
545 case SIGQUIT:
546 if (! signame[0])
547 snprintf (signame, sizeof (signame), "SIGQUIT");
548 eerrorx ("%s: caught %s, aborting", applet, signame);
549 case SIGUSR1:
550 eerror ("rc: Aborting!");
551 /* Kill any running services we have started */
552
553 signal (SIGCHLD, SIG_IGN);
554 for (pl = service_pids; pl; pl = pl->next)
555 kill (pl->pid, SIGTERM);
556
557 /* Notify plugins we are aborting */
558 rc_plugin_run (rc_hook_abort, NULL);
559
560 /* Only drop into single user mode if we're booting */
561 run = getenv ("RUNLEVEL");
562 prev = getenv ("PREVLEVEL");
563 if ((prev &&
564 (strcmp (prev, "S") == 0 ||
565 strcmp (prev, "1") == 0)) ||
566 (run &&
567 (strcmp (run, "S") == 0 ||
568 strcmp (run, "1") == 0)))
569 single_user ();
570
571 exit (EXIT_FAILURE);
572 break;
573
574 default:
575 eerror ("%s: caught unknown signal %d", applet, sig);
576 }
577
578 /* Restore errno */
579 errno = serrno;
580 }
581
582 int main (int argc, char **argv)
583 {
584 char *RUNLEVEL = NULL;
585 char *PREVLEVEL = NULL;
586 char *runlevel = NULL;
587 char *newlevel = NULL;
588 char *service = NULL;
589 char **deporder = NULL;
590 int i = 0;
591 int j = 0;
592 bool going_down = false;
593 bool interactive = false;
594 int depoptions = RC_DEP_STRICT | RC_DEP_TRACE;
595 char ksoftbuffer [PATH_MAX];
596 char pidstr[6];
597
598 if (argv[0])
599 applet = rc_xstrdup (basename (argv[0]));
600
601 if (! applet)
602 eerrorx ("arguments required");
603
604 argc--;
605 argv++;
606
607 /* Handle multicall stuff */
608 if (applet[0] == 'e' || (applet[0] == 'v' && applet[1] == 'e'))
609 exit (do_e (argc, argv));
610
611 if (strncmp (applet, "service_", strlen ("service_")) == 0)
612 exit (do_service (argc, argv));
613
614 if (strcmp (applet, "get_options") == 0 ||
615 strcmp (applet, "save_options") == 0)
616 exit (do_options (argc, argv));
617
618 if (strncmp (applet, "mark_service_", strlen ("mark_service_")) == 0)
619 exit (do_mark_service (argc, argv));
620
621 if (strcmp (applet, "is_runlevel_start") == 0)
622 exit (rc_runlevel_starting () ? 0 : 1);
623 else if (strcmp (applet, "is_runlevel_stop") == 0)
624 exit (rc_runlevel_stopping () ? 0 : 1);
625
626 if (strcmp (applet, "rc-abort") == 0) {
627 char *p = getenv ("RC_PID");
628 pid_t pid = 0;
629
630 if (p && sscanf (p, "%d", &pid) == 1) {
631 if (kill (pid, SIGUSR1) != 0)
632 eerrorx ("rc-abort: failed to signal parent %d: %s",
633 pid, strerror (errno));
634 exit (EXIT_SUCCESS);
635 }
636 exit (EXIT_FAILURE);
637 }
638
639 if (strcmp (applet, "rc" ) != 0)
640 eerrorx ("%s: unknown applet", applet);
641
642 /* OK, so we really are the main RC process
643 Only root should be able to run us */
644 if (geteuid () != 0)
645 eerrorx ("%s: root access required", applet);
646
647 atexit (cleanup);
648 newlevel = argv[0];
649
650 /* Setup a signal handler */
651 signal (SIGINT, handle_signal);
652 signal (SIGQUIT, handle_signal);
653 signal (SIGTERM, handle_signal);
654 signal (SIGUSR1, handle_signal);
655
656 /* Ensure our environment is pure
657 Also, add our configuration to it */
658 env = rc_filter_env ();
659 env = rc_config_env (env);
660
661 if (env) {
662 char *p;
663
664 #ifdef __linux__
665 /* clearenv isn't portable, but there's no harm in using it
666 if we have it */
667 clearenv ();
668 #else
669 char *var;
670 /* No clearenv present here then.
671 We could manipulate environ directly ourselves, but it seems that
672 some kernels bitch about this according to the environ man pages
673 so we walk though environ and call unsetenv for each value. */
674 while (environ[0]) {
675 tmp = rc_xstrdup (environ[0]);
676 p = tmp;
677 var = strsep (&p, "=");
678 unsetenv (var);
679 free (tmp);
680 }
681 tmp = NULL;
682 #endif
683
684 STRLIST_FOREACH (env, p, i)
685 if (strcmp (p, "RC_SOFTLEVEL") != 0 && strcmp (p, "SOFTLEVEL") != 0)
686 putenv (p);
687
688 /* We don't free our list as that would be null in environ */
689 }
690
691 /* Enable logging */
692 setenv ("RC_ELOG", "rc", 1);
693
694 /* Export our PID */
695 snprintf (pidstr, sizeof (pidstr), "%d", getpid ());
696 setenv ("RC_PID", pidstr, 1);
697
698 interactive = rc_exists (INTERACTIVE);
699 rc_plugin_load ();
700
701 /* RUNLEVEL is set by sysvinit as is a magic number
702 RC_SOFTLEVEL is set by us and is the name for this magic number
703 even though all our userland documentation refers to runlevel */
704 RUNLEVEL = getenv ("RUNLEVEL");
705 PREVLEVEL = getenv ("PREVLEVEL");
706
707 if (RUNLEVEL && newlevel) {
708 if (strcmp (RUNLEVEL, "S") == 0 || strcmp (RUNLEVEL, "1") == 0) {
709 /* OK, we're either in runlevel 1 or single user mode */
710 if (strcmp (newlevel, RC_LEVEL_SYSINIT) == 0) {
711 struct utsname uts;
712 pid_t pid;
713 pid_t wpid;
714 int status = 0;
715 #ifdef __linux__
716 FILE *fp;
717 #endif
718
719 /* exec init-early.sh if it exists
720 * This should just setup the console to use the correct
721 * font. Maybe it should setup the keyboard too? */
722 if (rc_exists (INITEARLYSH)) {
723 if ((pid = vfork ()) == -1)
724 eerrorx ("%s: vfork: %s", applet, strerror (errno));
725
726 if (pid == 0) {
727 execl (INITEARLYSH, INITEARLYSH, (char *) NULL);
728 eerror ("%s: unable to exec `" INITEARLYSH "': %s",
729 applet, strerror (errno));
730 _exit (EXIT_FAILURE);
731 }
732
733 do {
734 wpid = waitpid (pid, &status, 0);
735 if (wpid < 1)
736 eerror ("waitpid: %s", strerror (errno));
737 } while (! WIFEXITED (status) && ! WIFSIGNALED (status));
738 }
739
740 uname (&uts);
741
742 printf ("\n");
743 printf (" %sGentoo/%s; %shttp://www.gentoo.org/%s"
744 "\n Copyright 1999-2007 Gentoo Foundation; "
745 "Distributed under the GPLv2\n\n",
746 ecolor (ecolor_good), uts.sysname, ecolor (ecolor_bracket),
747 ecolor (ecolor_normal));
748
749 if (rc_is_env ("RC_INTERACTIVE", "yes"))
750 printf ("Press %sI%s to enter interactive boot mode\n\n",
751 ecolor (ecolor_good), ecolor (ecolor_normal));
752
753 setenv ("RC_SOFTLEVEL", newlevel, 1);
754 rc_plugin_run (rc_hook_runlevel_start_in, newlevel);
755
756 if ((pid = vfork ()) == -1)
757 eerrorx ("%s: vfork: %s", applet, strerror (errno));
758
759 if (pid == 0) {
760 execl (INITSH, INITSH, (char *) NULL);
761 eerror ("%s: unable to exec `" INITSH "': %s",
762 applet, strerror (errno));
763 _exit (EXIT_FAILURE);
764 }
765
766 do {
767 wpid = waitpid (pid, &status, 0);
768 if (wpid < 1)
769 eerror ("waitpid: %s", strerror (errno));
770 } while (! WIFEXITED (status) && ! WIFSIGNALED (status));
771
772 if (! WIFEXITED (status) || ! WEXITSTATUS (status) == 0)
773 exit (EXIT_FAILURE);
774
775 /* If we requested a softlevel, save it now */
776 #ifdef __linux__
777 set_ksoftlevel (NULL);
778
779 if ((fp = fopen ("/proc/cmdline", "r"))) {
780 char buffer[RC_LINEBUFFER];
781 char *soft;
782
783 memset (buffer, 0, sizeof (buffer));
784 if (fgets (buffer, RC_LINEBUFFER, fp) &&
785 (soft = strstr (buffer, "softlevel=")))
786 {
787 i = soft - buffer;
788 if (i == 0 || buffer[i - 1] == ' ') {
789 char *level;
790
791 /* Trim the trailing carriage return if present */
792 i = strlen (buffer) - 1;
793 if (buffer[i] == '\n')
794 buffer[i] = 0;
795
796 soft += strlen ("softlevel=");
797 level = strsep (&soft, " ");
798 set_ksoftlevel (level);
799 }
800 }
801 fclose (fp);
802 }
803 #endif
804 rc_plugin_run (rc_hook_runlevel_start_out, newlevel);
805
806 if (want_interactive ())
807 mark_interactive ();
808
809 exit (EXIT_SUCCESS);
810 }
811
812 #ifdef __linux__
813 /* Parse the inittab file so we can work out the level to telinit */
814 if (strcmp (newlevel, RC_LEVEL_BOOT) != 0 &&
815 strcmp (newlevel, RC_LEVEL_SINGLE) != 0)
816 {
817 char **inittab = rc_get_list (NULL, "/etc/inittab");
818 char *line;
819 char *p;
820 char *token;
821 char lvl[2] = {0, 0};
822
823 STRLIST_FOREACH (inittab, line, i) {
824 p = line;
825 token = strsep (&p, ":");
826 if (! token || token[0] != 'l')
827 continue;
828
829 if ((token = strsep (&p, ":")) == NULL)
830 continue;
831
832 /* Snag the level */
833 lvl[0] = token[0];
834
835 /* The name is spaced after this */
836 if ((token = strsep (&p, " ")) == NULL)
837 continue;
838
839 if ((token = strsep (&p, " ")) == NULL)
840 continue;
841
842 if (strcmp (token, newlevel) == 0)
843 break;
844 }
845 rc_strlist_free (inittab);
846
847 /* We have a level, so telinit into it */
848 if (lvl[0] == 0) {
849 eerrorx ("%s: couldn't find a runlevel called `%s'",
850 applet, newlevel);
851 } else {
852 execl ("/sbin/telinit", "/sbin/telinit", lvl, (char *) NULL);
853 eerrorx ("%s: unable to exec `/sbin/telinit': %s",
854 applet, strerror (errno));
855 }
856 }
857 #endif
858 }
859 }
860
861 /* Check we're in the runlevel requested, ie from
862 rc single
863 rc shutdown
864 rc reboot
865 */
866 if (newlevel) {
867 if (strcmp (newlevel, RC_LEVEL_SINGLE) == 0) {
868 if (! RUNLEVEL ||
869 (strcmp (RUNLEVEL, "S") != 0 &&
870 strcmp (RUNLEVEL, "1") != 0))
871 {
872 /* Remember the current runlevel for when we come back */
873 set_ksoftlevel (runlevel);
874 single_user ();
875 }
876 } else if (strcmp (newlevel, RC_LEVEL_REBOOT) == 0) {
877 if (! RUNLEVEL ||
878 strcmp (RUNLEVEL, "6") != 0)
879 {
880 execl ("/sbin/shutdown", "/sbin/shutdown", "-r", "now", (char *) NULL);
881 eerrorx ("%s: unable to exec `/sbin/shutdown': %s",
882 applet, strerror (errno));
883 }
884 } else if (strcmp (newlevel, RC_LEVEL_SHUTDOWN) == 0) {
885 if (! RUNLEVEL ||
886 strcmp (RUNLEVEL, "0") != 0)
887 {
888 execl ("/sbin/shutdown", "/sbin/shutdown",
889 #ifdef __linux
890 "-h",
891 #else
892 "-p",
893 #endif
894 "now", (char *) NULL);
895 eerrorx ("%s: unable to exec `/sbin/shutdown': %s",
896 applet, strerror (errno));
897 }
898 }
899 }
900
901 /* Export our current softlevel */
902 runlevel = rc_get_runlevel ();
903
904 /* Now we start handling our children */
905 signal (SIGCHLD, handle_signal);
906
907 /* If we're in the default runlevel and ksoftlevel exists, we should use
908 that instead */
909 if (newlevel &&
910 rc_exists (RC_SVCDIR "ksoftlevel") &&
911 strcmp (newlevel, RC_LEVEL_DEFAULT) == 0)
912 {
913 /* We should only use ksoftlevel if we were in single user mode
914 If not, we need to erase ksoftlevel now. */
915 if (PREVLEVEL &&
916 (strcmp (PREVLEVEL, "1") == 0 ||
917 strcmp (PREVLEVEL, "S") == 0 ||
918 strcmp (PREVLEVEL, "N") == 0))
919 {
920 FILE *fp;
921
922 if (! (fp = fopen (RC_SVCDIR "ksoftlevel", "r")))
923 eerror ("fopen `%s': %s", RC_SVCDIR "ksoftlevel",
924 strerror (errno));
925 else {
926 if (fgets (ksoftbuffer, sizeof (ksoftbuffer), fp)) {
927 i = strlen (ksoftbuffer) - 1;
928 if (ksoftbuffer[i] == '\n')
929 ksoftbuffer[i] = 0;
930 newlevel = ksoftbuffer;
931 }
932 fclose (fp);
933 }
934 } else
935 set_ksoftlevel (NULL);
936 }
937
938 if (newlevel &&
939 (strcmp (newlevel, RC_LEVEL_REBOOT) == 0 ||
940 strcmp (newlevel, RC_LEVEL_SHUTDOWN) == 0 ||
941 strcmp (newlevel, RC_LEVEL_SINGLE) == 0))
942 {
943 going_down = true;
944 rc_set_runlevel (newlevel);
945 setenv ("RC_SOFTLEVEL", newlevel, 1);
946 rc_plugin_run (rc_hook_runlevel_stop_in, newlevel);
947 } else {
948 rc_plugin_run (rc_hook_runlevel_stop_in, runlevel);
949 }
950
951 /* Check if runlevel is valid if we're changing */
952 if (newlevel && strcmp (runlevel, newlevel) != 0 && ! going_down) {
953 tmp = rc_strcatpaths (RC_RUNLEVELDIR, newlevel, (char *) NULL);
954 if (! rc_is_dir (tmp))
955 eerrorx ("%s: is not a valid runlevel", newlevel);
956 CHAR_FREE (tmp);
957 }
958
959 /* Load our deptree now */
960 if ((deptree = rc_load_deptree ()) == NULL)
961 eerrorx ("failed to load deptree");
962
963 /* Clean the failed services state dir now */
964 if (rc_is_dir (RC_SVCDIR "failed"))
965 rc_rm_dir (RC_SVCDIR "failed", false);
966
967 mkdir (RC_SVCDIR "/softscripts.new", 0755);
968
969 #ifdef __linux__
970 /* udev likes to start services before we're ready when it does
971 its coldplugging thing. runscript knows when we're not ready so it
972 stores a list of coldplugged services in DEVBOOT for us to pick up
973 here when we are ready for them */
974 if (rc_is_dir (DEVBOOT)) {
975 start_services = rc_ls_dir (NULL, DEVBOOT, RC_LS_INITD);
976 rc_rm_dir (DEVBOOT, true);
977
978 STRLIST_FOREACH (start_services, service, i)
979 if (rc_allow_plug (service))
980 rc_mark_service (service, rc_service_coldplugged);
981 /* We need to dump this list now.
982 This may seem redunant, but only Linux needs this and saves on
983 code bloat. */
984 rc_strlist_free (start_services);
985 start_services = NULL;
986 }
987 #else
988 /* BSD's on the other hand populate /dev automagically and use devd.
989 The only downside of this approach and ours is that we have to hard code
990 the device node to the init script to simulate the coldplug into
991 runlevel for our dependency tree to work. */
992 if (newlevel && strcmp (newlevel, RC_LEVEL_BOOT) == 0 &&
993 (strcmp (runlevel, RC_LEVEL_SINGLE) == 0 ||
994 strcmp (runlevel, RC_LEVEL_SYSINIT) == 0) &&
995 rc_is_env ("RC_COLDPLUG", "yes"))
996 {
997 /* The net interfaces are easy - they're all in net /dev/net :) */
998 start_services = rc_ls_dir (NULL, "/dev/net", 0);
999 STRLIST_FOREACH (start_services, service, i) {
1000 j = (strlen ("net.") + strlen (service) + 1);
1001 tmp = rc_xmalloc (sizeof (char *) * j);
1002 snprintf (tmp, j, "net.%s", service);
1003 if (rc_service_exists (tmp) && rc_allow_plug (tmp))
1004 rc_mark_service (tmp, rc_service_coldplugged);
1005 CHAR_FREE (tmp);
1006 }
1007 rc_strlist_free (start_services);
1008
1009 /* The mice are a little more tricky.
1010 If we coldplug anything else, we'll probably do it here. */
1011 start_services = rc_ls_dir (NULL, "/dev", 0);
1012 STRLIST_FOREACH (start_services, service, i) {
1013 if (strncmp (service, "psm", 3) == 0 ||
1014 strncmp (service, "ums", 3) == 0)
1015 {
1016 char *p = service + 3;
1017 if (p && isdigit (*p)) {
1018 j = (strlen ("moused.") + strlen (service) + 1);
1019 tmp = rc_xmalloc (sizeof (char *) * j);
1020 snprintf (tmp, j, "moused.%s", service);
1021 if (rc_service_exists (tmp) && rc_allow_plug (tmp))
1022 rc_mark_service (tmp, rc_service_coldplugged);
1023 CHAR_FREE (tmp);
1024 }
1025 }
1026 }
1027 rc_strlist_free (start_services);
1028 start_services = NULL;
1029 }
1030 #endif
1031
1032 /* Build a list of all services to stop and then work out the
1033 correct order for stopping them */
1034 stop_services = rc_ls_dir (stop_services, RC_SVCDIR_STARTING, RC_LS_INITD);
1035 stop_services = rc_ls_dir (stop_services, RC_SVCDIR_INACTIVE, RC_LS_INITD);
1036 stop_services = rc_ls_dir (stop_services, RC_SVCDIR_STARTED, RC_LS_INITD);
1037
1038 types = rc_strlist_add (NULL, "ineed");
1039 types = rc_strlist_add (types, "iuse");
1040 types = rc_strlist_add (types, "iafter");
1041 deporder = rc_get_depends (deptree, types, stop_services,
1042 runlevel, depoptions);
1043 rc_strlist_free (stop_services);
1044 rc_strlist_free (types);
1045 stop_services = deporder;
1046 deporder = NULL;
1047 types = NULL;
1048 rc_strlist_reverse (stop_services);
1049
1050 /* Load our list of coldplugged services */
1051 coldplugged_services = rc_ls_dir (coldplugged_services,
1052 RC_SVCDIR_COLDPLUGGED, RC_LS_INITD);
1053
1054 /* Load our start services now.
1055 We have different rules dependent on runlevel. */
1056 if (newlevel && strcmp (newlevel, RC_LEVEL_BOOT) == 0) {
1057 if (coldplugged_services) {
1058 einfon ("Device initiated services:");
1059 STRLIST_FOREACH (coldplugged_services, service, i) {
1060 printf (" %s", service);
1061 start_services = rc_strlist_add (start_services, service);
1062 }
1063 printf ("\n");
1064 }
1065 tmp = rc_strcatpaths (RC_RUNLEVELDIR, newlevel ? newlevel : runlevel,
1066 (char *) NULL);
1067 start_services = rc_ls_dir (start_services, tmp, RC_LS_INITD);
1068 CHAR_FREE (tmp);
1069 } else {
1070 /* Store our list of coldplugged services */
1071 coldplugged_services = rc_ls_dir (coldplugged_services, RC_SVCDIR_COLDPLUGGED,
1072 RC_LS_INITD);
1073 if (strcmp (newlevel ? newlevel : runlevel, RC_LEVEL_SINGLE) != 0 &&
1074 strcmp (newlevel ? newlevel : runlevel, RC_LEVEL_SHUTDOWN) != 0 &&
1075 strcmp (newlevel ? newlevel : runlevel, RC_LEVEL_REBOOT) != 0)
1076 {
1077 /* We need to include the boot runlevel services if we're not in it */
1078 start_services = rc_ls_dir (start_services, RC_RUNLEVELDIR RC_LEVEL_BOOT,
1079 RC_LS_INITD);
1080 STRLIST_FOREACH (coldplugged_services, service, i)
1081 start_services = rc_strlist_add (start_services, service);
1082
1083 tmp = rc_strcatpaths (RC_RUNLEVELDIR,
1084 newlevel ? newlevel : runlevel, (char *) NULL);
1085 start_services = rc_ls_dir (start_services, tmp, RC_LS_INITD);
1086 CHAR_FREE (tmp);
1087 }
1088 }
1089
1090 /* Save out softlevel now */
1091 if (going_down)
1092 rc_set_runlevel (newlevel);
1093
1094 types = rc_strlist_add (NULL, "needsme");
1095 types = rc_strlist_add (types, "usesme");
1096 /* Now stop the services that shouldn't be running */
1097 STRLIST_FOREACH (stop_services, service, i) {
1098 bool found = false;
1099 char *conf = NULL;
1100 char **stopdeps = NULL;
1101 char *svc1 = NULL;
1102 char *svc2 = NULL;
1103 int k;
1104
1105 if (rc_service_state (service, rc_service_stopped))
1106 continue;
1107
1108 /* We always stop the service when in these runlevels */
1109 if (going_down) {
1110 pid_t pid = rc_stop_service (service);
1111 if (pid > 0 && ! rc_is_env ("RC_PARALLEL", "yes"))
1112 rc_waitpid (pid);
1113 continue;
1114 }
1115
1116 /* If we're in the start list then don't bother stopping us */
1117 STRLIST_FOREACH (start_services, svc1, j)
1118 if (strcmp (svc1, service) == 0) {
1119 found = true;
1120 break;
1121 }
1122
1123 /* Unless we would use a different config file */
1124 if (found) {
1125 int len;
1126 if (! newlevel)
1127 continue;
1128
1129 len = strlen (service) + strlen (runlevel) + 2;
1130 tmp = rc_xmalloc (sizeof (char *) * len);
1131 snprintf (tmp, len, "%s.%s", service, runlevel);
1132 conf = rc_strcatpaths (RC_CONFDIR, tmp, (char *) NULL);
1133 found = rc_exists (conf);
1134 CHAR_FREE (conf);
1135 CHAR_FREE (tmp);
1136 if (! found) {
1137 len = strlen (service) + strlen (newlevel) + 2;
1138 tmp = rc_xmalloc (sizeof (char *) * len);
1139 snprintf (tmp, len, "%s.%s", service, newlevel);
1140 conf = rc_strcatpaths (RC_CONFDIR, tmp, (char *) NULL);
1141 found = rc_exists (conf);
1142 CHAR_FREE (conf);
1143 CHAR_FREE (tmp);
1144 if (!found)
1145 continue;
1146 }
1147 } else {
1148 /* Allow coldplugged services not to be in the runlevels list */
1149 if (rc_service_state (service, rc_service_coldplugged))
1150 continue;
1151 }
1152
1153 /* We got this far! Or last check is to see if any any service that
1154 going to be started depends on us */
1155 stopdeps = rc_strlist_add (stopdeps, service);
1156 deporder = rc_get_depends (deptree, types, stopdeps,
1157 runlevel, RC_DEP_STRICT);
1158 rc_strlist_free (stopdeps);
1159 stopdeps = NULL;
1160 found = false;
1161 STRLIST_FOREACH (deporder, svc1, j) {
1162 STRLIST_FOREACH (start_services, svc2, k)
1163 if (strcmp (svc1, svc2) == 0) {
1164 found = true;
1165 break;
1166 }
1167 if (found)
1168 break;
1169 }
1170 rc_strlist_free (deporder);
1171 deporder = NULL;
1172
1173 /* After all that we can finally stop the blighter! */
1174 if (! found) {
1175 pid_t pid = rc_stop_service (service);
1176 if (pid > 0 && ! rc_is_env ("RC_PARALLEL", "yes"))
1177 rc_waitpid (pid);
1178 }
1179 }
1180 rc_strlist_free (types);
1181 types = NULL;
1182
1183 /* Wait for our services to finish */
1184 wait_for_services ();
1185
1186 /* Notify the plugins we have finished */
1187 rc_plugin_run (rc_hook_runlevel_stop_out, runlevel);
1188
1189 rmdir (RC_SVCDIR "/softscripts.new");
1190
1191 /* Store the new runlevel */
1192 if (newlevel) {
1193 rc_set_runlevel (newlevel);
1194 runlevel = newlevel;
1195 setenv ("RC_SOFTLEVEL", runlevel, 1);
1196 }
1197
1198 /* Run the halt script if needed */
1199 if (strcmp (runlevel, RC_LEVEL_SHUTDOWN) == 0 ||
1200 strcmp (runlevel, RC_LEVEL_REBOOT) == 0)
1201 {
1202 execl (HALTSH, HALTSH, runlevel, (char *) NULL);
1203 eerrorx ("%s: unable to exec `%s': %s",
1204 applet, HALTSH, strerror (errno));
1205 }
1206
1207 /* Single user is done now */
1208 if (strcmp (runlevel, RC_LEVEL_SINGLE) == 0) {
1209 if (rc_exists (INTERACTIVE))
1210 unlink (INTERACTIVE);
1211 sulogin (false);
1212 }
1213
1214 mkdir (RC_SVCDIR "softscripts.old", 0755);
1215 rc_plugin_run (rc_hook_runlevel_start_in, runlevel);
1216
1217 /* Re-add our coldplugged services if they stopped */
1218 STRLIST_FOREACH (coldplugged_services, service, i)
1219 rc_mark_service (service, rc_service_coldplugged);
1220
1221 /* Order the services to start */
1222 types = rc_strlist_add (NULL, "ineed");
1223 types = rc_strlist_add (types, "iuse");
1224 types = rc_strlist_add (types, "iafter");
1225 deporder = rc_get_depends (deptree, types, start_services,
1226 runlevel, depoptions);
1227 rc_strlist_free (types);
1228 types = NULL;
1229 rc_strlist_free (start_services);
1230 start_services = deporder;
1231 deporder = NULL;
1232
1233 STRLIST_FOREACH (start_services, service, i) {
1234 if (rc_service_state (service, rc_service_stopped)) {
1235 pid_t pid;
1236
1237 if (! interactive)
1238 interactive = want_interactive ();
1239
1240 if (interactive) {
1241 interactive_retry:
1242 printf ("\n");
1243 einfo ("About to start the service %s", service);
1244 eindent ();
1245 einfo ("1) Start the service\t\t2) Skip the service");
1246 einfo ("3) Continue boot process\t\t4) Exit to shell");
1247 eoutdent ();
1248 interactive_option:
1249 switch (read_key (true)) {
1250 case '1': break;
1251 case '2': continue;
1252 case '3': interactive = false; break;
1253 case '4': sulogin (true); goto interactive_retry;
1254 default: goto interactive_option;
1255 }
1256 }
1257
1258 /* Remember the pid if we're running in parallel */
1259 if ((pid = rc_start_service (service)))
1260 add_pid (pid);
1261
1262 if (! rc_is_env ("RC_PARALLEL", "yes")) {
1263 rc_waitpid (pid);
1264 remove_pid (pid);
1265 }
1266 }
1267 }
1268
1269 /* Wait for our services to finish */
1270 wait_for_services ();
1271
1272 rc_plugin_run (rc_hook_runlevel_start_out, runlevel);
1273
1274 /* Store our interactive status for boot */
1275 if (interactive && strcmp (runlevel, RC_LEVEL_BOOT) == 0)
1276 mark_interactive ();
1277 else {
1278 if (rc_exists (INTERACTIVE))
1279 unlink (INTERACTIVE);
1280 }
1281
1282 return (EXIT_SUCCESS);
1283 }
1284
ViewVC Help
Powered by ViewVC 1.1.20
|
{
"url": "https://sources.gentoo.org/cgi-bin/viewvc.cgi/baselayout/trunk/src/rc.c?revision=2700&view=markup&pathrev=2703",
"source_domain": "sources.gentoo.org",
"snapshot_id": "crawl=CC-MAIN-2017-22",
"warc_metadata": {
"Content-Length": "409891",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:VT6CPF5ZMSFW4PONPIDVMFVRU5RDAY3C",
"WARC-Concurrent-To": "<urn:uuid:9a786125-23fc-4605-b371-f31bd711cfb9>",
"WARC-Date": "2017-05-24T23:31:57Z",
"WARC-IP-Address": "140.211.166.190",
"WARC-Identified-Payload-Type": "application/xhtml+xml",
"WARC-Payload-Digest": "sha1:WAV77SY2WX4UUL6LK2YUXBDUOH6BUJ2R",
"WARC-Record-ID": "<urn:uuid:6163656f-3b91-435a-a606-cebb314b87ca>",
"WARC-Target-URI": "https://sources.gentoo.org/cgi-bin/viewvc.cgi/baselayout/trunk/src/rc.c?revision=2700&view=markup&pathrev=2703",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:af6361d2-2bbf-49a5-94b2-c80698a33eb9>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-185-224-210.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2017-22\r\noperator: Common Crawl Admin\r\ndescription: Wide crawl of the web for May 2017\r\npublisher: Common Crawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
29,
36,
37,
65,
66,
128,
129,
130,
186,
242,
270,
295,
330,
335,
342,
410,
459,
461,
534,
603,
653,
655,
691,
719,
725,
728,
754,
779,
807,
832,
854,
876,
899,
922,
946,
968,
991,
1014,
1037,
1061,
1084,
1087,
1109,
1128,
1152,
1178,
1202,
1205,
1246,
1298,
1337,
1372,
1375,
1427,
1479,
1529,
1587,
1590,
1637,
1640,
1674,
1677,
1711,
1754,
1773,
1792,
1797,
1800,
1826,
1829,
1860,
1889,
1921,
1967,
2006,
2046,
2086,
2117,
2145,
2148,
2188,
2191,
2217,
2222,
2236,
2261,
2277,
2319,
2322,
2352,
2357,
2390,
2393,
2417,
2420,
2443,
2495,
2519,
2524,
2527,
2543,
2571,
2585,
2596,
2601,
2604,
2630,
2659,
2702,
2738,
2775,
2805,
2834,
2838,
2883,
2932,
2983,
3032,
3083,
3087,
3106,
3112,
3116,
3160,
3166,
3197,
3208,
3223,
3249,
3262,
3284,
3288,
3336,
3424,
3450,
3476,
3501,
3529,
3558,
3587,
3612,
3618,
3622,
3662,
3699,
3736,
3772,
3778,
3798,
3813,
3853,
3873,
3900,
3911,
3923,
3935,
3941,
3947,
3956,
3983,
3989,
3993,
4013,
4044,
4075,
4079,
4109,
4126,
4130,
4163,
4178,
4194,
4237,
4264,
4270,
4282,
4288,
4292,
4309,
4338,
4342,
4381,
4407,
4452,
4479,
4523,
4549,
4594,
4621,
4668,
4695,
4711,
4761,
4789,
4805,
4852,
4879,
4922,
4955,
4999,
5033,
5078,
5105,
5151,
5179,
5224,
5251,
5297,
5325,
5371,
5399,
5443,
5477,
5522,
5557,
5603,
5619,
5666,
5683,
5730,
5747,
5795,
5813,
5858,
5873,
5884,
5927,
5954,
5960,
5964,
5977,
5993,
6010,
6030,
6051,
6057,
6061,
6111,
6117,
6138,
6142,
6198,
6248,
6252,
6301,
6358,
6412,
6469,
6524,
6582,
6637,
6695,
6750,
6808,
6866,
6927,
6985,
7046,
7109,
7126,
7144,
7178,
7238,
7252,
7263,
7307,
7311,
7358,
7364,
7368,
7423,
7429,
7450,
7490,
7494,
7550,
7600,
7604,
7658,
7714,
7773,
7829,
7889,
7946,
8006,
8063,
8123,
8180,
8243,
8303,
8312,
8356,
8360,
8438,
8499,
8558,
8613,
8630,
8649,
8660,
8664,
8730,
8763,
8813,
8849,
8853,
8918,
8944,
8985,
9008,
9037,
9044,
9072,
9125,
9154,
9204,
9261,
9279,
9285,
9289,
9336,
9342,
9346,
9396,
9402,
9423,
9463,
9467,
9486,
9536,
9540,
9596,
9645,
9649,
9696,
9719,
9749,
9808,
9820,
9847,
9900,
9960,
9969,
10013,
10017,
10064,
10070,
10074,
10112,
10118,
10146,
10162,
10166,
10199,
10219,
10223,
10300,
10366,
10392,
10449,
10493,
10499,
10503,
10543,
10584,
10599,
10627,
10638,
10666,
10695,
10701,
10750,
10754,
10786,
10790,
10843,
10847,
10863,
10869,
10873,
10913,
10919,
10931,
10935,
10982,
11002,
11006,
11032,
11084,
11090,
11094,
11134,
11140,
11181,
11193,
11210,
11216,
11220,
11256,
11262,
11283,
11316,
11320,
11363,
11402,
11463,
11542,
11548,
11559,
11563,
11594,
11598,
11614,
11634,
11655,
11698,
11709,
11713,
11739,
11743,
11762,
11819,
11839,
11860,
11873,
11932,
11941,
11995,
11999,
12059,
12082,
12092,
12150,
12206,
12229,
12240,
12266,
12272,
12303,
12316,
12335,
12405,
12487,
12497,
12522,
12533,
12539,
12545,
12549,
12584,
12590,
12611,
12677,
12732,
12763,
12773,
12805,
12868,
12899,
12924,
12935,
12941,
12945,
12999,
13005,
13019,
13023,
13045,
13090,
13137,
13183,
13189,
13235,
13277,
13351,
13363,
13369,
13373,
13429,
13502,
13514,
13520,
13524,
13558,
13575,
13581,
13585,
13622,
13628,
13648,
13682,
13688,
13692,
13728,
13734,
13768,
13782,
13803,
13822,
13870,
13889,
13900,
13957,
13997,
14016,
14022,
14026,
14065,
14071,
14099,
14118,
14122,
14171,
14197,
14211,
14238,
14247,
14276,
14291,
14302,
14308,
14323,
14329,
14335,
14339,
14379,
14385,
14409,
14442,
14457,
14473,
14492,
14507,
14527,
14531,
14550,
14568,
14577,
14619,
14638,
14663,
14709,
14721,
14727,
14789,
14793,
14833,
14850,
14872,
14883,
14887,
14904,
14926,
14978,
14996,
15018,
15071,
15089,
15111,
15164,
15222,
15240,
15270,
15322,
15326,
15357,
15404,
15433,
15437,
15478,
15519,
15523,
15582,
15613,
15646,
15663,
15695,
15728,
15740,
15771,
15801,
15821,
15825,
15850,
15861,
15865,
15878,
15936,
15942,
15946,
15970,
15990,
15996,
16000,
16037,
16043,
16070,
16098,
16125,
16152,
16178,
16206,
16221,
16236,
16265,
16295,
16346,
16379,
16399,
16403,
16420,
16466,
16470,
16488,
16524,
16528,
16540,
16552,
16556,
16589,
16657,
16687,
16691,
16755,
16791,
16795,
16842,
16884,
16920,
16924,
16998,
17039,
17043,
17094,
17138,
17193,
17237,
17241,
17285,
17318,
17337,
17341,
17385,
17419,
17476,
17504,
17529,
17535,
17560,
17566,
17570,
17607,
17651,
17655,
17703,
17745,
17770,
17820,
17824,
17846,
17870,
17874,
17907,
17943,
17980,
18017,
18054,
18058,
18096,
18137,
18165,
18196,
18200,
18215,
18228,
18232,
18253,
18317,
18338,
18355,
18365,
18380,
18418,
18488,
18557,
18624,
18649,
18684,
18697,
18725,
18745,
18761,
18767,
18783,
18794,
18798,
18830,
18903,
18919,
18923,
18989,
18995,
18999,
19024,
19057,
19061,
19086,
19143,
19177,
19181,
19224,
19247,
19251,
19307,
19375,
19444,
19480,
19518,
19522,
19554,
19624,
19685,
19737,
19761,
19776,
19792,
19812,
19833,
19847,
19858,
19862,
19901,
19961,
20016,
20051,
20083,
20140,
20144,
20164,
20217,
20273,
20304,
20330,
20336,
20340,
20349,
20387,
20405,
20451,
20513,
20519,
20523,
20541,
20545,
20564,
20619,
20668,
20707,
20771,
20800,
20804,
20849,
20911,
20962,
20966,
21008,
21065,
21069,
21101,
21158,
21162,
21182,
21225,
21276,
21307,
21333,
21339,
21343,
21352,
21390,
21408,
21454,
21516,
21520,
21581,
21606,
21610,
21661,
21682,
21709,
21713,
21760,
21792,
21808,
21812,
21853,
21898,
21942,
21948,
21971,
22013,
22030,
22034,
22089,
22118,
22145,
22164,
22168,
22203,
22236,
22264,
22270,
22276,
22293,
22299,
22310,
22368,
22372,
22401,
22426,
22430,
22455,
22461,
22465,
22486,
22559,
22608,
22653,
22659,
22716,
22732,
22745,
22762,
22788,
22792,
22833,
22847,
22877,
22913,
22927,
22931,
22975,
22989,
22993,
23018,
23041,
23045,
23085,
23129,
23143,
23147,
23191,
23205,
23209,
23248,
23259,
23265,
23296,
23300,
23346,
23369,
23426,
23449,
23462,
23528,
23583,
23614,
23620,
23626,
23637,
23643,
23649,
23653,
23707,
23721,
23737,
23751,
23758,
23778,
23829,
23851,
23887,
23921,
23927,
23989,
24020,
24040,
24046,
24104,
24126,
24159,
24165,
24241,
24297,
24328,
24334,
24394,
24416,
24449,
24455,
24502,
24521,
24531,
24541,
24551,
24562,
24589,
24645,
24676,
24682,
24688,
24694,
24698,
24737,
24772,
24776,
24821,
24858,
24862,
24939,
24959,
24979,
25021,
25067,
25073,
25141,
25189,
25210,
25247,
25283,
25318,
25324,
25338,
25342,
25396,
25450,
25473,
25484,
25541,
25575,
25607,
25631,
25659,
25665,
25682,
25688,
25699,
25726,
25732,
25736,
25756,
25804,
25853,
25899,
25905,
25928,
25960,
26002,
26058,
26071,
26127,
26133,
26137,
26192,
26264,
26332,
26359,
26414,
26435,
26441,
26445,
26476,
26524,
26564,
26568,
26618,
26658,
26701,
26705,
26753,
26757,
26778,
26846,
26917,
26988,
27027,
27058,
27119,
27150,
27154,
27203,
27236,
27291,
27329,
27396,
27415,
27453,
27480,
27486,
27496,
27569,
27646,
27715,
27764,
27825,
27873,
27922,
27960,
27966,
28037,
28091,
28142,
28193,
28238,
28281,
28338,
28390,
28412,
28419,
28458,
28463,
28506,
28571,
28622,
28674,
28719,
28758,
28765,
28793,
28823,
28877,
28922,
28968,
29025,
29077,
29099,
29106,
29113,
29120,
29159,
29187,
29194,
29206,
29211,
29278,
29318,
29399,
29480,
29560,
29565,
29610,
29655,
29702,
29765,
29793,
29831,
29861,
29892,
29914,
29933,
29974,
29979,
30028,
30089,
30131,
30136,
30173,
30228,
30290,
30323,
30367,
30425,
30455,
30519,
30526,
30546,
30553,
30628,
30649,
30717,
30739,
30753,
30803,
30887,
30906,
30980,
31052,
31120,
31127,
31203,
31282,
31301,
31357,
31421,
31426,
31469,
31522,
31590,
31612,
31619,
31626,
31631,
31665,
31686,
31719,
31724,
31771,
31818,
31877,
31928,
31953,
31977,
32006,
32030,
32054,
32066,
32071,
32128,
32143,
32148,
32210,
32233,
32277,
32333,
32356,
32371,
32378,
32383,
32451,
32498,
32538,
32557,
32569,
32576,
32581,
32636,
32654,
32668,
32689,
32704,
32709,
32762,
32809,
32863,
32924,
32955,
32978,
33000,
33020,
33073,
33120,
33174,
33235,
33266,
33289,
33311,
33328,
33343,
33350,
33364,
33434,
33495,
33510,
33517,
33522,
33595,
33637,
33689,
33747,
33778,
33811,
33833,
33853,
33896,
33943,
33980,
33999,
34011,
34018,
34034,
34046,
34053,
34086,
34108,
34113,
34173,
34193,
34237,
34293,
34316,
34323,
34330,
34360,
34379,
34384,
34427,
34454,
34459,
34506,
34564,
34569,
34612,
34617,
34651,
34672,
34705,
34731,
34774,
34781,
34786,
34827,
34881,
34927,
34934,
34988,
35033,
35073,
35080,
35085,
35120,
35172,
35206,
35233,
35255,
35262,
35267,
35315,
35373,
35378,
35437,
35493,
35549,
35554,
35593,
35638,
35683,
35730,
35794,
35822,
35852,
35871,
35910,
35942,
35964,
35969,
36021,
36080,
36096,
36101,
36125,
36165,
36170,
36194,
36218,
36238,
36293,
36310,
36370,
36431,
36449,
36474,
36506,
36528,
36553,
36596,
36651,
36690,
36697,
36704,
36709,
36766,
36811,
36831,
36836,
36883,
36906,
36929,
36936,
36943,
36950,
36955,
36998,
37025,
37030,
37089,
37094,
37143,
37206,
37232,
37244,
37278,
37305,
37312,
37317,
37345,
37352,
37357,
37358,
37372
],
"line_end_idx": [
29,
36,
37,
65,
66,
128,
129,
130,
186,
242,
270,
295,
330,
335,
342,
410,
459,
461,
534,
603,
653,
655,
691,
719,
725,
728,
754,
779,
807,
832,
854,
876,
899,
922,
946,
968,
991,
1014,
1037,
1061,
1084,
1087,
1109,
1128,
1152,
1178,
1202,
1205,
1246,
1298,
1337,
1372,
1375,
1427,
1479,
1529,
1587,
1590,
1637,
1640,
1674,
1677,
1711,
1754,
1773,
1792,
1797,
1800,
1826,
1829,
1860,
1889,
1921,
1967,
2006,
2046,
2086,
2117,
2145,
2148,
2188,
2191,
2217,
2222,
2236,
2261,
2277,
2319,
2322,
2352,
2357,
2390,
2393,
2417,
2420,
2443,
2495,
2519,
2524,
2527,
2543,
2571,
2585,
2596,
2601,
2604,
2630,
2659,
2702,
2738,
2775,
2805,
2834,
2838,
2883,
2932,
2983,
3032,
3083,
3087,
3106,
3112,
3116,
3160,
3166,
3197,
3208,
3223,
3249,
3262,
3284,
3288,
3336,
3424,
3450,
3476,
3501,
3529,
3558,
3587,
3612,
3618,
3622,
3662,
3699,
3736,
3772,
3778,
3798,
3813,
3853,
3873,
3900,
3911,
3923,
3935,
3941,
3947,
3956,
3983,
3989,
3993,
4013,
4044,
4075,
4079,
4109,
4126,
4130,
4163,
4178,
4194,
4237,
4264,
4270,
4282,
4288,
4292,
4309,
4338,
4342,
4381,
4407,
4452,
4479,
4523,
4549,
4594,
4621,
4668,
4695,
4711,
4761,
4789,
4805,
4852,
4879,
4922,
4955,
4999,
5033,
5078,
5105,
5151,
5179,
5224,
5251,
5297,
5325,
5371,
5399,
5443,
5477,
5522,
5557,
5603,
5619,
5666,
5683,
5730,
5747,
5795,
5813,
5858,
5873,
5884,
5927,
5954,
5960,
5964,
5977,
5993,
6010,
6030,
6051,
6057,
6061,
6111,
6117,
6138,
6142,
6198,
6248,
6252,
6301,
6358,
6412,
6469,
6524,
6582,
6637,
6695,
6750,
6808,
6866,
6927,
6985,
7046,
7109,
7126,
7144,
7178,
7238,
7252,
7263,
7307,
7311,
7358,
7364,
7368,
7423,
7429,
7450,
7490,
7494,
7550,
7600,
7604,
7658,
7714,
7773,
7829,
7889,
7946,
8006,
8063,
8123,
8180,
8243,
8303,
8312,
8356,
8360,
8438,
8499,
8558,
8613,
8630,
8649,
8660,
8664,
8730,
8763,
8813,
8849,
8853,
8918,
8944,
8985,
9008,
9037,
9044,
9072,
9125,
9154,
9204,
9261,
9279,
9285,
9289,
9336,
9342,
9346,
9396,
9402,
9423,
9463,
9467,
9486,
9536,
9540,
9596,
9645,
9649,
9696,
9719,
9749,
9808,
9820,
9847,
9900,
9960,
9969,
10013,
10017,
10064,
10070,
10074,
10112,
10118,
10146,
10162,
10166,
10199,
10219,
10223,
10300,
10366,
10392,
10449,
10493,
10499,
10503,
10543,
10584,
10599,
10627,
10638,
10666,
10695,
10701,
10750,
10754,
10786,
10790,
10843,
10847,
10863,
10869,
10873,
10913,
10919,
10931,
10935,
10982,
11002,
11006,
11032,
11084,
11090,
11094,
11134,
11140,
11181,
11193,
11210,
11216,
11220,
11256,
11262,
11283,
11316,
11320,
11363,
11402,
11463,
11542,
11548,
11559,
11563,
11594,
11598,
11614,
11634,
11655,
11698,
11709,
11713,
11739,
11743,
11762,
11819,
11839,
11860,
11873,
11932,
11941,
11995,
11999,
12059,
12082,
12092,
12150,
12206,
12229,
12240,
12266,
12272,
12303,
12316,
12335,
12405,
12487,
12497,
12522,
12533,
12539,
12545,
12549,
12584,
12590,
12611,
12677,
12732,
12763,
12773,
12805,
12868,
12899,
12924,
12935,
12941,
12945,
12999,
13005,
13019,
13023,
13045,
13090,
13137,
13183,
13189,
13235,
13277,
13351,
13363,
13369,
13373,
13429,
13502,
13514,
13520,
13524,
13558,
13575,
13581,
13585,
13622,
13628,
13648,
13682,
13688,
13692,
13728,
13734,
13768,
13782,
13803,
13822,
13870,
13889,
13900,
13957,
13997,
14016,
14022,
14026,
14065,
14071,
14099,
14118,
14122,
14171,
14197,
14211,
14238,
14247,
14276,
14291,
14302,
14308,
14323,
14329,
14335,
14339,
14379,
14385,
14409,
14442,
14457,
14473,
14492,
14507,
14527,
14531,
14550,
14568,
14577,
14619,
14638,
14663,
14709,
14721,
14727,
14789,
14793,
14833,
14850,
14872,
14883,
14887,
14904,
14926,
14978,
14996,
15018,
15071,
15089,
15111,
15164,
15222,
15240,
15270,
15322,
15326,
15357,
15404,
15433,
15437,
15478,
15519,
15523,
15582,
15613,
15646,
15663,
15695,
15728,
15740,
15771,
15801,
15821,
15825,
15850,
15861,
15865,
15878,
15936,
15942,
15946,
15970,
15990,
15996,
16000,
16037,
16043,
16070,
16098,
16125,
16152,
16178,
16206,
16221,
16236,
16265,
16295,
16346,
16379,
16399,
16403,
16420,
16466,
16470,
16488,
16524,
16528,
16540,
16552,
16556,
16589,
16657,
16687,
16691,
16755,
16791,
16795,
16842,
16884,
16920,
16924,
16998,
17039,
17043,
17094,
17138,
17193,
17237,
17241,
17285,
17318,
17337,
17341,
17385,
17419,
17476,
17504,
17529,
17535,
17560,
17566,
17570,
17607,
17651,
17655,
17703,
17745,
17770,
17820,
17824,
17846,
17870,
17874,
17907,
17943,
17980,
18017,
18054,
18058,
18096,
18137,
18165,
18196,
18200,
18215,
18228,
18232,
18253,
18317,
18338,
18355,
18365,
18380,
18418,
18488,
18557,
18624,
18649,
18684,
18697,
18725,
18745,
18761,
18767,
18783,
18794,
18798,
18830,
18903,
18919,
18923,
18989,
18995,
18999,
19024,
19057,
19061,
19086,
19143,
19177,
19181,
19224,
19247,
19251,
19307,
19375,
19444,
19480,
19518,
19522,
19554,
19624,
19685,
19737,
19761,
19776,
19792,
19812,
19833,
19847,
19858,
19862,
19901,
19961,
20016,
20051,
20083,
20140,
20144,
20164,
20217,
20273,
20304,
20330,
20336,
20340,
20349,
20387,
20405,
20451,
20513,
20519,
20523,
20541,
20545,
20564,
20619,
20668,
20707,
20771,
20800,
20804,
20849,
20911,
20962,
20966,
21008,
21065,
21069,
21101,
21158,
21162,
21182,
21225,
21276,
21307,
21333,
21339,
21343,
21352,
21390,
21408,
21454,
21516,
21520,
21581,
21606,
21610,
21661,
21682,
21709,
21713,
21760,
21792,
21808,
21812,
21853,
21898,
21942,
21948,
21971,
22013,
22030,
22034,
22089,
22118,
22145,
22164,
22168,
22203,
22236,
22264,
22270,
22276,
22293,
22299,
22310,
22368,
22372,
22401,
22426,
22430,
22455,
22461,
22465,
22486,
22559,
22608,
22653,
22659,
22716,
22732,
22745,
22762,
22788,
22792,
22833,
22847,
22877,
22913,
22927,
22931,
22975,
22989,
22993,
23018,
23041,
23045,
23085,
23129,
23143,
23147,
23191,
23205,
23209,
23248,
23259,
23265,
23296,
23300,
23346,
23369,
23426,
23449,
23462,
23528,
23583,
23614,
23620,
23626,
23637,
23643,
23649,
23653,
23707,
23721,
23737,
23751,
23758,
23778,
23829,
23851,
23887,
23921,
23927,
23989,
24020,
24040,
24046,
24104,
24126,
24159,
24165,
24241,
24297,
24328,
24334,
24394,
24416,
24449,
24455,
24502,
24521,
24531,
24541,
24551,
24562,
24589,
24645,
24676,
24682,
24688,
24694,
24698,
24737,
24772,
24776,
24821,
24858,
24862,
24939,
24959,
24979,
25021,
25067,
25073,
25141,
25189,
25210,
25247,
25283,
25318,
25324,
25338,
25342,
25396,
25450,
25473,
25484,
25541,
25575,
25607,
25631,
25659,
25665,
25682,
25688,
25699,
25726,
25732,
25736,
25756,
25804,
25853,
25899,
25905,
25928,
25960,
26002,
26058,
26071,
26127,
26133,
26137,
26192,
26264,
26332,
26359,
26414,
26435,
26441,
26445,
26476,
26524,
26564,
26568,
26618,
26658,
26701,
26705,
26753,
26757,
26778,
26846,
26917,
26988,
27027,
27058,
27119,
27150,
27154,
27203,
27236,
27291,
27329,
27396,
27415,
27453,
27480,
27486,
27496,
27569,
27646,
27715,
27764,
27825,
27873,
27922,
27960,
27966,
28037,
28091,
28142,
28193,
28238,
28281,
28338,
28390,
28412,
28419,
28458,
28463,
28506,
28571,
28622,
28674,
28719,
28758,
28765,
28793,
28823,
28877,
28922,
28968,
29025,
29077,
29099,
29106,
29113,
29120,
29159,
29187,
29194,
29206,
29211,
29278,
29318,
29399,
29480,
29560,
29565,
29610,
29655,
29702,
29765,
29793,
29831,
29861,
29892,
29914,
29933,
29974,
29979,
30028,
30089,
30131,
30136,
30173,
30228,
30290,
30323,
30367,
30425,
30455,
30519,
30526,
30546,
30553,
30628,
30649,
30717,
30739,
30753,
30803,
30887,
30906,
30980,
31052,
31120,
31127,
31203,
31282,
31301,
31357,
31421,
31426,
31469,
31522,
31590,
31612,
31619,
31626,
31631,
31665,
31686,
31719,
31724,
31771,
31818,
31877,
31928,
31953,
31977,
32006,
32030,
32054,
32066,
32071,
32128,
32143,
32148,
32210,
32233,
32277,
32333,
32356,
32371,
32378,
32383,
32451,
32498,
32538,
32557,
32569,
32576,
32581,
32636,
32654,
32668,
32689,
32704,
32709,
32762,
32809,
32863,
32924,
32955,
32978,
33000,
33020,
33073,
33120,
33174,
33235,
33266,
33289,
33311,
33328,
33343,
33350,
33364,
33434,
33495,
33510,
33517,
33522,
33595,
33637,
33689,
33747,
33778,
33811,
33833,
33853,
33896,
33943,
33980,
33999,
34011,
34018,
34034,
34046,
34053,
34086,
34108,
34113,
34173,
34193,
34237,
34293,
34316,
34323,
34330,
34360,
34379,
34384,
34427,
34454,
34459,
34506,
34564,
34569,
34612,
34617,
34651,
34672,
34705,
34731,
34774,
34781,
34786,
34827,
34881,
34927,
34934,
34988,
35033,
35073,
35080,
35085,
35120,
35172,
35206,
35233,
35255,
35262,
35267,
35315,
35373,
35378,
35437,
35493,
35549,
35554,
35593,
35638,
35683,
35730,
35794,
35822,
35852,
35871,
35910,
35942,
35964,
35969,
36021,
36080,
36096,
36101,
36125,
36165,
36170,
36194,
36218,
36238,
36293,
36310,
36370,
36431,
36449,
36474,
36506,
36528,
36553,
36596,
36651,
36690,
36697,
36704,
36709,
36766,
36811,
36831,
36836,
36883,
36906,
36929,
36936,
36943,
36950,
36955,
36998,
37025,
37030,
37089,
37094,
37143,
37206,
37232,
37244,
37278,
37305,
37312,
37317,
37345,
37352,
37357,
37358,
37372,
37398
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 37398,
"ccnet_original_nlines": 1299,
"rps_doc_curly_bracket": 0.005882670171558857,
"rps_doc_ldnoobw_words": 1,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.10939213633537292,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.03675663843750954,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.5848145484924316,
"rps_doc_frac_unique_words": 0.39765626192092896,
"rps_doc_mean_word_length": 4.947851657867432,
"rps_doc_num_sentences": 145,
"rps_doc_symbol_to_word_ratio": 0.0065832799300551414,
"rps_doc_unigram_entropy": 6.570342063903809,
"rps_doc_word_count": 5120,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.07527731359004974,
"rps_doc_frac_chars_dupe_6grams": 0.03564520925283432,
"rps_doc_frac_chars_dupe_7grams": 0.01188173983246088,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.01800023950636387,
"rps_doc_frac_chars_top_3gram": 0.024316109716892242,
"rps_doc_frac_chars_top_4gram": 0.024158209562301636,
"rps_doc_books_importance": -4010.22607421875,
"rps_doc_books_importance_length_correction": -4010.22607421875,
"rps_doc_openwebtext_importance": -2055.46728515625,
"rps_doc_openwebtext_importance_length_correction": -2055.46728515625,
"rps_doc_wikipedia_importance": -1112.704345703125,
"rps_doc_wikipedia_importance_length_correction": -1112.704345703125
},
"fasttext": {
"dclm": 0.6721680164337158,
"english": 0.3578260540962219,
"fineweb_edu_approx": 2.477586507797241,
"eai_general_math": 0.26229745149612427,
"eai_open_web_math": 0.32007545232772827,
"eai_web_code": 0.32829028367996216
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.455",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.02",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "4",
"label": "Analyze"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "4",
"label": "Code/Software"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "3",
"label": "Academic Writing"
}
},
"reasoning_depth": {
"primary": {
"code": "4",
"label": "Advanced Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "4",
"label": "Graduate/Expert Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-4,935,870,550,370,730,000
|
JSON REST API: Validate multiple responses against a DataSource
kktulasi404kktulasi404 Posts: 10
Hi All,
I am trying to validate the JSON response against an Excel sheet for each INPUT value passed.
I am using the JSON assertor and for each attribute have assigned the corresponding column name of the Excel.
But, for the attributes where it is a ARRAY/LIST or TABLE of values it is failed saying no value found.
SAMPLE FILE:
INPUT|OUTPUT_STRING1|OUTPUT_STRING2|OUTPUT_LIST1 |OUTPUT_LIST2
1|AB|JK|"A", "B", "C"|"D", "H"
2|CD|LM|"O|"L", "H","M"
3|EF|GF||"L"
Comments
• kktulasi404kktulasi404 Posts: 10
Sample JSON o/p: {
"PV_COLUMN" : null,
"PV_ARRAY_COLUMN_PARENT" :
[
{
"CHILD_COL1" : "XC",
"CHILD_COL2" : "TEST",
"CHILD_COL3" : null
},
{
"CHILD_COL1" : "ER",
"CHILD_COL2" : "TEST",
"CHILD_COL3" : "18-JAN-2017"
}
]
}
• OmarROmarR Posts: 224 admin
Good Morning kktulasi404 :)
sips coffee
Depending on the type of assertion you wish to make (E.g, Value, Structure, etc) , you will need to ensure you select the appropriate node in the JSON tree.
In my example below, I wish to create a "String Comparison" Assertion, therefore, I will need to select the appropriate element node that contains a string value. SOAtest makes it easy to identify the eligible nodes (Element Values) by placing an "S" next to the node. Similarly, if you were to create an "Occurrence" Assertion, SOAtest would place an "O" next to the eligible nodes (Element names).
• kktulasi404kktulasi404 Posts: 10
Thanks Omar. I have selected the Value Occurrence assertion but it says Input value is not an Integer.
In Excel Sheet: I have given values as below and parameterized in the URL for the input_value and JSON assertor for the o/p values.
So, the first input will return two rows similarly if I have 2nd input in row 3 then I will again have multiple rows.
INPUT_VALUE|COLA|COLB|COLC
1|A|B||
|E|F|18-JAN-2017|
So, when I pass value 1 as parameter I am expecting two records.
My JSON response o/p is -
{
"INPUT_VALUE" : null,
"OUTPUT_TAB" : [
{
"COLA" : "A",
"COLB" : "B",
"COLC" : null
},
{
"COLA" : "E",
"COLB" : "F",
"COLC" : "18-JAN-2017"
}
]
}
Tree looks like
I have seen some exampled for using multiple sheets for the child records is that can be applicable for JSON assertor?
• sunkarabhanusunkarabhanu Posts: 8
Hi Omar, Do you have a solution of this post? I have the same issue and would like to find the steps needed to solve it.
• OmarROmarR Posts: 224 admin
edited August 2017
Good morning fellow SOAtest users!
Thank you very much for clarifying your use case. In order to assert the values of repeated Child Elements in Sequence, we will need to take the time to implement the steps required for such an assertion. Below are the steps to accomplish this. Please refer to the screenshot below as you implement your scenario to confirm your setup is correct. This will work for both XML and JSON payloads by using the appropriate tools.
STEPS:
1) Extract the desired Element values in Sequence using a JSON databank and store them in a writable-datasource. This will isolate the desired values you wish to Assert. **Note: **you will need to modify the XPATH to extract all of the repeated elements in the sequence. When "Evaluating the Xpath", ensure that all the element values are shown in the "Result" Window".
2) Run your .tst thus far to ensure that your extracted Values are populated in the Writable-datasource successfully.
3) Now, in order for your JSON Assertor to assert the Extracted Element values, we will need to pass the Writable-datasource values through a Request. We do this by adding a new Test Suite to your current .tst and adding a Messaging client to it. We then Parameterize the payload with the values stored in the Writable-datasource.
For example, choose Literal for your Input mode in your Request and insert some JSON content like the following:
{"data": ""}
After inserting a payload similiar to the one above, Change your input-mode to FORM-JSON. This will now allow you to Parameterize your Data values with the values in your Writable Datasource.
Similiary, for XML payloads, you could insert <data/>in Literal mode and then change to FORM-XML.
4) Set your Messaging Client's Transport to NONE. By setting the transport to NONE, we are configuring the Messaging Client to run any tools (Databank, Assertor, etc) associated with the test, but our actual request will NOT be sent anywhere. By selecting NONE for our transport, we are essentially saying "Do-not-send-to-an-Endpoint, just execute my chained tools!"
5) Chain a JSON assertor to the Messaging Client.
Please ensure that the assertor is chained to the output of the "request traffic" of the Messaging client.
6) Run your .tst to populate the assertor and configure it to assert against the values from your Table of Expected Values.
7) Finally, Navigate to the Top Parent Test Suite>Execution Options>Advanced Options and select Flat (Lockstep) for your Multiple Data Source Iteration. This will allow for Test execution to iterate over rows in different data sources together at the same time MEANING it will assert the rows from the table of expected values against the Writable-datasource in order!
Please try this on your end and let me know if you run into any trouble with any specific step! I would appreciate your feedback on this.
• kktulasi404kktulasi404 Posts: 10
Thank you will try and let you know
• kktulasi404kktulasi404 Posts: 10
I have tried the above steps at Step 6 it is giving error as Invalid JSON.
• OmarROmarR Posts: 224 admin
Within your JSON Assertor, under the "Expected JSON" tab, what does the output look like? Would you kindly post a screenshot of the payload shown in Literal mode?
• kktulasi404kktulasi404 Posts: 10
Hi Omar,
Attached is the Messaging Client Structure. In the JSON assertor nothing is been displayed for now as the messaging client is not executed.
When executed the Invalid JSON error occurred.
• saileesailee Posts: 7
@OmarR :
I did above steps and in expected JSON tab of JSON assertor , i am getting blank root i.e. {}
Could you please reply what will be the issue in this case.
error message i m getting is :
Error Message:
DataSource: Actual_Data(Extracted) (row 1): Invalid JSON
Additional Details:
Source: Messaging Client Output
• OmarROmarR Posts: 224 admin
Good morning Sailee,
Please ensure that the assertor is chained to the output of the "request traffic" of the Messaging client.
• saileesailee Posts: 7
edited August 2017
Thank you so much @OmarR . its worked.
My next step is to pass value from data source and fetch the response in another data source. I am using java class to pass query from data source to my database connectivity java class and now i want to pass this database response value to excel sheet in data source.but in extension tool at time i can pass only one data source.
I want to call multiple data source in one test case.
• jakubiakjakubiak Posts: 664 admin
I am not sure how your tests are set up - but is it possible to set up a Text or XML Data Bank that extracts the value from the result of your database query? Data banks store values in a type of "virtual" data source that can be accessed by column name even if you have a specific explicit data source configured in your test.
• saileesailee Posts: 7
no , I am passing result of database query into excel sheet. and compare to above scenario my "expected Data" is in excel as data source.
I want to know how can I send "Database Account" properties in my extension tool having java class so that i can use 1 java class to run multiple databases by fetching database property.
• jakubiakjakubiak Posts: 664 admin
Is this your scenario: you have a Database Account property specified in your .tst file. You also have an Extension Tool that uses a Java class to make a database query. You would like the Java class to use the same database settings as you have specified in your Database Account?
If this is the case, I would put the data that you have specified in your Database Account into environment variables. Then, instead of specifying the values directly in the Database Account, you would use the ${varName} syntax to reference the environment variables. Then in your Java class, you can use the Parasoft API com.parasoft.api.ScriptingContext.getEnvironmentVariableValue() to reference the same environment variables. The nice thing about this approach is you can then modify the environment variables, and both places in your scenario will get the updated values.
If I have misunderstood your scenario, please clarify.
• saileesailee Posts: 7
Hi @jakubiak : thank you so much for your explanation. I tried above steps and did some more R&D , I don't see use of database account in my case as i am going to pass it from environment variables in my java code. also Mongo DB does not support connectivity in soatest using database account or DB.tst or datasource as database.
My next step is to map actual json and expected (database ) response using jsonpath in excel sheet and validate it in only one excel sheet. i.e. means my datasource will be one excel sheet for actual and expected response.
Let me know your thoughts on this.
• Ireneusz SzmigielIreneusz Szmigiel Posts: 213 ✭✭✭
edited August 2017
• saileesailee Posts: 7
I am getting actual response in json and mongodb database response is in json.
I want to compare these two responses using json path in excel sheet. and pass this result to soatest to make test pass/fail as per validation
• jakubiakjakubiak Posts: 664 admin
Trying a single excel sheet seems like a good way to go - let us know how it works for you!
• saileesailee Posts: 7
edited September 2017
Hi @jakubiak as I have written in above i have created draft REST API automation framework.
I have created one utility class which will have three methods:
1. getactualResponse : i will fetch data from the class which will have response from writable datasource
2. getExpectedRepsosne : i will fetch data from the my generic class for mongodb connectivity.
3. CompareActualExpected : using if else i will compare actul and expected resp using jsonpath.
public Object getExpectedResponseFromDB () throws Exception, SQLException
{
Object str=*mongoDB.getKeywords( input, context);* //got null pointer exception
Application.showMessage("str: " + str);
return str;
}
I got stuck here ....
I want to call below method which i have written in mongodb
public static Object getKeywords(Object input,ExtensionToolContext context)
throws SQLException, JSONException {
//String URL_MONGODB = context.getEnvironmentVariableValue("URL_MONGODB");
int PORT_MONGODB = Integer.parseInt(context.getEnvironmentVariableValue("PORT_MONGODB"));
.............................
please suggest how can I call above method in my utility class,.
Is this correct approach.
Thank you in advance.
• jakubiakjakubiak Posts: 664 admin
What is the name of the class that has the getKeywords() method? It looks to me like you are not referencing it correctly - try referencing it using the fully qualified name of the class, for example com.company.mypackage.MongoDB.
• vashi83vashi83 Posts: 1
edited February 2018
Hi OmarR,
I followed all the steps you mentioned and it worked fine for the first time.
When I run the whole test sequentially again. it is not asserting all the values but only the first one.
any suggestion will be of great help.
Sign In or Register to comment.
|
{
"url": "https://forums.parasoft.com/discussion/comment/7424/",
"source_domain": "forums.parasoft.com",
"snapshot_id": "crawl=CC-MAIN-2020-29",
"warc_metadata": {
"Content-Length": "75733",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:33N5N66IA727BC25Z2URJEXNEBQBGDJP",
"WARC-Concurrent-To": "<urn:uuid:8114173d-7460-4d79-a5ef-1bfe146619b9>",
"WARC-Date": "2020-07-04T04:33:15Z",
"WARC-IP-Address": "162.159.128.79",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:LV2SX5QXC2ZZTFW4QPOLH6MJXVE4TN5B",
"WARC-Record-ID": "<urn:uuid:16e074c0-fdc9-44fb-9959-c32d6a810d48>",
"WARC-Target-URI": "https://forums.parasoft.com/discussion/comment/7424/",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:a8dfa921-dc28-4cf8-aeb5-7634add4ff5b>"
},
"warc_info": "isPartOf: CC-MAIN-2020-29\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for July 2020\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-83.ec2.internal\r\nsoftware: Apache Nutch 1.17 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.2-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
64,
65,
98,
99,
107,
108,
202,
203,
313,
417,
418,
431,
432,
495,
526,
550,
563,
564,
573,
574,
611,
612,
635,
659,
690,
696,
702,
727,
754,
778,
785,
791,
816,
843,
876,
882,
888,
894,
895,
927,
928,
960,
961,
977,
978,
1139,
1140,
1544,
1545,
1582,
1583,
1690,
1691,
1827,
1949,
1950,
1981,
1993,
2015,
2016,
2085,
2115,
2121,
2147,
2168,
2174,
2192,
2210,
2228,
2235,
2241,
2259,
2277,
2304,
2310,
2316,
2322,
2342,
2343,
2466,
2467,
2505,
2506,
2631,
2632,
2664,
2687,
2688,
2727,
2728,
3157,
3158,
3169,
3170,
3544,
3545,
3667,
3668,
4003,
4120,
4137,
4138,
4334,
4335,
4437,
4438,
4809,
4810,
4864,
4975,
4976,
5104,
5105,
5478,
5479,
5621,
5622,
5659,
5660,
5700,
5701,
5738,
5739,
5818,
5819,
5851,
5852,
6019,
6020,
6057,
6058,
6071,
6072,
6216,
6267,
6268,
6294,
6295,
6308,
6406,
6470,
6471,
6506,
6525,
6586,
6587,
6611,
6647,
6648,
6680,
6681,
6706,
6707,
6818,
6819,
6845,
6868,
6869,
6912,
7247,
7305,
7306,
7344,
7345,
7677,
7678,
7704,
7705,
7847,
8038,
8039,
8077,
8078,
8364,
8365,
8947,
8948,
9007,
9008,
9034,
9035,
9369,
9370,
9597,
9598,
9637,
9638,
9692,
9715,
9741,
9742,
9825,
9972,
9973,
10011,
10012,
10108,
10109,
10135,
10161,
10162,
10258,
10326,
10436,
10535,
10635,
10713,
10719,
10720,
10810,
10858,
10878,
10883,
10889,
10894,
10895,
10921,
10985,
11065,
11106,
11185,
11279,
11280,
11314,
11383,
11413,
11414,
11440,
11441,
11479,
11480,
11715,
11716,
11744,
11769,
11770,
11784,
11866,
11975,
11976,
12018,
12019
],
"line_end_idx": [
64,
65,
98,
99,
107,
108,
202,
203,
313,
417,
418,
431,
432,
495,
526,
550,
563,
564,
573,
574,
611,
612,
635,
659,
690,
696,
702,
727,
754,
778,
785,
791,
816,
843,
876,
882,
888,
894,
895,
927,
928,
960,
961,
977,
978,
1139,
1140,
1544,
1545,
1582,
1583,
1690,
1691,
1827,
1949,
1950,
1981,
1993,
2015,
2016,
2085,
2115,
2121,
2147,
2168,
2174,
2192,
2210,
2228,
2235,
2241,
2259,
2277,
2304,
2310,
2316,
2322,
2342,
2343,
2466,
2467,
2505,
2506,
2631,
2632,
2664,
2687,
2688,
2727,
2728,
3157,
3158,
3169,
3170,
3544,
3545,
3667,
3668,
4003,
4120,
4137,
4138,
4334,
4335,
4437,
4438,
4809,
4810,
4864,
4975,
4976,
5104,
5105,
5478,
5479,
5621,
5622,
5659,
5660,
5700,
5701,
5738,
5739,
5818,
5819,
5851,
5852,
6019,
6020,
6057,
6058,
6071,
6072,
6216,
6267,
6268,
6294,
6295,
6308,
6406,
6470,
6471,
6506,
6525,
6586,
6587,
6611,
6647,
6648,
6680,
6681,
6706,
6707,
6818,
6819,
6845,
6868,
6869,
6912,
7247,
7305,
7306,
7344,
7345,
7677,
7678,
7704,
7705,
7847,
8038,
8039,
8077,
8078,
8364,
8365,
8947,
8948,
9007,
9008,
9034,
9035,
9369,
9370,
9597,
9598,
9637,
9638,
9692,
9715,
9741,
9742,
9825,
9972,
9973,
10011,
10012,
10108,
10109,
10135,
10161,
10162,
10258,
10326,
10436,
10535,
10635,
10713,
10719,
10720,
10810,
10858,
10878,
10883,
10889,
10894,
10895,
10921,
10985,
11065,
11106,
11185,
11279,
11280,
11314,
11383,
11413,
11414,
11440,
11441,
11479,
11480,
11715,
11716,
11744,
11769,
11770,
11784,
11866,
11975,
11976,
12018,
12019,
12050
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 12050,
"ccnet_original_nlines": 242,
"rps_doc_curly_bracket": 0.0017427400453016162,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.36094674468040466,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.06255283206701279,
"rps_doc_frac_lines_end_with_ellipsis": 0.008230449631810188,
"rps_doc_frac_no_alph_words": 0.22273880243301392,
"rps_doc_frac_unique_words": 0.28944504261016846,
"rps_doc_mean_word_length": 4.866158962249756,
"rps_doc_num_sentences": 118,
"rps_doc_symbol_to_word_ratio": 0.004226540215313435,
"rps_doc_unigram_entropy": 5.507072448730469,
"rps_doc_word_count": 1838,
"rps_doc_frac_chars_dupe_10grams": 0.01923076994717121,
"rps_doc_frac_chars_dupe_5grams": 0.07133273780345917,
"rps_doc_frac_chars_dupe_6grams": 0.04002682864665985,
"rps_doc_frac_chars_dupe_7grams": 0.03533095121383667,
"rps_doc_frac_chars_dupe_8grams": 0.01923076994717121,
"rps_doc_frac_chars_dupe_9grams": 0.01923076994717121,
"rps_doc_frac_chars_top_2gram": 0.006149370223283768,
"rps_doc_frac_chars_top_3gram": 0.019454380497336388,
"rps_doc_frac_chars_top_4gram": 0.01274596992880106,
"rps_doc_books_importance": -1075.0850830078125,
"rps_doc_books_importance_length_correction": -1075.0850830078125,
"rps_doc_openwebtext_importance": -623.4191284179688,
"rps_doc_openwebtext_importance_length_correction": -623.4191284179688,
"rps_doc_wikipedia_importance": -406.2333068847656,
"rps_doc_wikipedia_importance_length_correction": -406.2333068847656
},
"fasttext": {
"dclm": 0.03268111124634743,
"english": 0.8449642658233643,
"fineweb_edu_approx": 1.5996906757354736,
"eai_general_math": 0.6315886378288269,
"eai_open_web_math": 0.2724909782409668,
"eai_web_code": 0.15623879432678223
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.776",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "4",
"label": "Analyze"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "4",
"label": "Missing Images or Figures"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "4",
"label": "Graduate/Expert Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
5,810,073,577,615,599,000
|
Ubuntu sunucuda uygulama yükleme hatasını [ÇÖZÜLDÜ]
• Admin
Ubuntu işletim sistemine sahip bir sunucuda apt ile uygulama yüklerken ‘E: Could not get lock /var/lib/dpkg/lock’ şeklinde bir hata alıyorsanız çözümü burada.
Ubuntu yüklü bir sunucuda apt veya apt-get komutu ile bir uygulama yüklerken aşağıdaki gibi bir hata ile karşılaştım.
E: Could not get lock /var/lib/dpkg/lock-frontend - open (11: Resource temporari ly unavailable)
E: Unable to acquire the dpkg frontend lock (/var/lib/dpkg/lock-frontend), is an other process using it?
[email protected]:~# sudo apt install nginx
E: Could not get lock /var/lib/dpkg/lock-frontend - open (11: Resource temporarily unavailable)
E: Unable to acquire the dpkg frontend lock (/var/lib/dpkg/lock-frontend), is another process using it?
Bu sorunun nedeni kilit dosyaları. Bu yüzden sistemden bu kilit dosyalarını sileceğiz. Bunu sorunu çözmek için aşağıdaki komutları teker teker çalıştırın.
sudo lsof /var/lib/dpkg/lock
sudo lsof /var/lib/apt/lists/lock
sudo lsof /var/cache/apt/archives/lock
Bu işlemin ardından paketleri yeniden yapılandırın.
sudo dpkg --configure -a
Bundan sonra “Unable to acquire the dpkg frontend lock” şeklinde bir uyarı görürseniz ise aşağıkdaki her bir komutu ayrı ayrı çalıştırın.
sudo kill -9 PID
sudo rm /var/lib/dpkg/lock-frontend
sudo apt update
Uygulama kurmaya çalışırken bu hatayı: "dpkg: error: dpkg frontend is locked by another process” alırsanız ise;
sudo lsof /var/lib/dpkg/lock-frontend
sudo kill -9 PID
sudo rm /var/lib/dpkg/lock-frontend
sudo dpkg --configure -a
komutlarını benzer şekilde tek tek çalıştırın ve sunucuyu yeniden başlatmak için reboot komutunu kullanın.
Sorun çözülmüş olmalı!
Benzer Konular
|
{
"url": "https://www.kurulumu.net/topic/46/ubuntu-sunucuda-uygulama-y%C3%BCkleme-hatas%C4%B1n%C4%B1-%C3%A7%C3%B6z%C3%BCld%C3%BC/1",
"source_domain": "www.kurulumu.net",
"snapshot_id": "crawl=CC-MAIN-2022-05",
"warc_metadata": {
"Content-Length": "108152",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:6ADDVKKRI57C5LMCW7HFDFZMEAOOXGWU",
"WARC-Concurrent-To": "<urn:uuid:afd9584f-5d8f-4e31-94b3-d4c66bee6c5a>",
"WARC-Date": "2022-01-21T09:11:47Z",
"WARC-IP-Address": "172.67.168.223",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:HI5FYI53GC3D6KFXNBNX65OLXTXGKM37",
"WARC-Record-ID": "<urn:uuid:8e9e4994-1904-4f2e-8e75-b7f3141064ce>",
"WARC-Target-URI": "https://www.kurulumu.net/topic/46/ubuntu-sunucuda-uygulama-y%C3%BCkleme-hatas%C4%B1n%C4%B1-%C3%A7%C3%B6z%C3%BCld%C3%BC/1",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:a5a1d616-d20b-44e1-a880-52baa8f8dcd1>"
},
"warc_info": "isPartOf: CC-MAIN-2022-05\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for January 2022\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-95\r\nsoftware: Apache Nutch 1.18 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.3-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
52,
53,
63,
64,
227,
228,
350,
351,
452,
561,
609,
709,
817,
822,
823,
982,
983,
1016,
1054,
1097,
1102,
1103,
1159,
1160,
1189,
1194,
1195,
1337,
1338,
1359,
1399,
1419,
1424,
1425,
1541,
1542,
1584,
1605,
1645,
1674,
1679,
1680,
1791,
1792,
1819,
1820,
1821,
1822,
1823
],
"line_end_idx": [
52,
53,
63,
64,
227,
228,
350,
351,
452,
561,
609,
709,
817,
822,
823,
982,
983,
1016,
1054,
1097,
1102,
1103,
1159,
1160,
1189,
1194,
1195,
1337,
1338,
1359,
1399,
1419,
1424,
1425,
1541,
1542,
1584,
1605,
1645,
1674,
1679,
1680,
1791,
1792,
1819,
1820,
1821,
1822,
1823,
1837
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 1837,
"ccnet_original_nlines": 49,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.0758807584643364,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.02168021909892559,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.28455284237861633,
"rps_doc_frac_unique_words": 0.5486725568771362,
"rps_doc_mean_word_length": 6.2522125244140625,
"rps_doc_num_sentences": 12,
"rps_doc_symbol_to_word_ratio": 0.002710029948502779,
"rps_doc_unigram_entropy": 4.5817131996154785,
"rps_doc_word_count": 226,
"rps_doc_frac_chars_dupe_10grams": 0.09907996654510498,
"rps_doc_frac_chars_dupe_5grams": 0.25194621086120605,
"rps_doc_frac_chars_dupe_6grams": 0.23496107757091522,
"rps_doc_frac_chars_dupe_7grams": 0.23496107757091522,
"rps_doc_frac_chars_dupe_8grams": 0.23496107757091522,
"rps_doc_frac_chars_dupe_9grams": 0.1726822406053543,
"rps_doc_frac_chars_top_2gram": 0.07360225915908813,
"rps_doc_frac_chars_top_3gram": 0.023354560136795044,
"rps_doc_frac_chars_top_4gram": 0.03184713050723076,
"rps_doc_books_importance": -95.91793060302734,
"rps_doc_books_importance_length_correction": -94.98822021484375,
"rps_doc_openwebtext_importance": -42.65867233276367,
"rps_doc_openwebtext_importance_length_correction": -42.65867233276367,
"rps_doc_wikipedia_importance": -29.646114349365234,
"rps_doc_wikipedia_importance_length_correction": -29.644386291503906
},
"fasttext": {
"dclm": 0.526665985584259,
"english": 0.034691859036684036,
"fineweb_edu_approx": 2.443631172180176,
"eai_general_math": 0.00032890000147745013,
"eai_open_web_math": 0.0018770700553432107,
"eai_web_code": 0.9736989736557007
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.462",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.02",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "23",
"label": "Tutorial"
},
"secondary": {
"code": "21",
"label": "Customer Support"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
4,351,816,192,180,339,700
|
Going Google
Jesse Chen • November 4, 2010 4 min read
Introduction#
One of the best things that one could do with their own domain, in my opinion, is to go Google. What I mean, by 'going Google', is setting up the web-based suite Google Apps on your own domain. For hobbyists like me who just wants a quick solution for hosting their own email or calendar domain, I think Google Apps is great.
Google Apps for Your Own Domain#
For example, how awesome is it to set up your own email domain, which in my case would be *@jessechen.net, to distinguish yourself from common peasants in the *@gmail.com, *@yahoo.com, or *@hotmail.com land? It gives you a nice brand to advertise yourself [or organization] and at the same time, makes your email incredibly unique. Setting up an email domain is easy nowadays with webmail packages such as SquirrelMail [oh god, not SquirrelMail], but I think it is safe to say that GMail is arguably the best web email client, if not the best email client ever. Some of the best features, in my opinion, are filters, gChat, keyboard shortcuts, and tight integration with contacts and tasks. The benefit of Google Apps is having your own email domain with your web email client being GMail. Heck, you can even design your own logo, making GMail pretty much your own unique customized email client.
See mine, for example.
creating your own customized GMail with Google Apps
What I particularly like about having my own email domain, is the ability to have a catch-all email address. The short version of what it does, is basically any incoming emails that are not sent to a known email address in the domain gets forwarded to an email address you specify. So, for example, when my friend, say his name was Thomas, wanted my email address to send me something. I simply created an email address on-the-fly for him, and told him to email me at thomas@jessechen.net. I will still get his email at my actual email address [since I specified my catch-all email address to be my personal one]. I know, that example is kind of silly and pointless, but what you can do with this ability is to create email addresses for all your subscription/registration purposes. That way, you can easily create filters for each website and/or detect which sites you have given your email address to started selling your address to spam [which you can easily block now with filters].
The Google Apps suite not only includes email, but also many others such as Google Calendar, Google Documents, Google Wave [sad to see it go], and Google Chat. You can create up to 50 email addresses I believe with the free edition. With that email address, you have access to only a few Google Products (edit: this has since changed). There really aren't that many products supported, so it is disappointing. However, there is a super secret Google Tested Truster beta program where they transition your Google Apps accounts into more full-fledged regular Google Accounts. I am currently in that beta program, and for me personally, I can use my *@jessechen.net address for my Youtube, Voice, Reader, Analytics, Adsense, Chrome, and on my Android device. The only negative is that Google checkout is not supported yet for Google Apps accounts, so on my Droid X I still have to set up my original Google account in order to buy apps in the Market. Hopefully, the paypal payment option will soon come into effect.
Conclusion#
The reason why I decided to write about Google Apps account and give them a glowing review is because of the huge impact it made. It streamlined my email, beforehand, I used to have an *@att.net, *@berkeley.edu, and *@gmail.com email that each had their own separate inboxes. I tried using Thunderbird for the longest time, but it never did grow on me. However, now I have one inbox, that is online so I can access it where ever I have Internet access, and I can send and receive all my emails all on one webpage, with my own unique email address domain. Not to mention, I can sign on to gChat and AIM in my GMail, thus making it one webpage for almost all of my online activity. Now, I know that I can reap most of the same benefits with a *@gmail.com address, but someone freaking took jesse.chen@gmail.com, and simply put, having an email address whose domain is your own name is pretty damn cool. I was just motivated to share this with anyone out there the ridiculous amount of benefits Google Apps have. I highly advise Google Apps, definitely set it up on your own domain if you can do so.
© 2021, Jesse Chen • 129489e
|
{
"url": "https://jessechen-o7r3fcsh0-0xjessel.vercel.app/posts/2010/going-google",
"source_domain": "jessechen-o7r3fcsh0-0xjessel.vercel.app",
"snapshot_id": "CC-MAIN-2024-22",
"warc_metadata": {
"Content-Length": "58383",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:TIKETYIFIMCFTDVF4DDJYSH57P5DVDQ5",
"WARC-Concurrent-To": "<urn:uuid:f47a6f98-1390-4bbc-97b4-d28f294d7632>",
"WARC-Date": "2024-05-28T15:56:57Z",
"WARC-IP-Address": "76.76.21.164",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:VJKA6ADMMAMOSFJKPONIAOPN6CTDXZAL",
"WARC-Record-ID": "<urn:uuid:2c2a7a19-38db-4b78-9628-678493d9f593>",
"WARC-Target-URI": "https://jessechen-o7r3fcsh0-0xjessel.vercel.app/posts/2010/going-google",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:ce185409-1b97-4288-a3a3-697de64750b0>"
},
"warc_info": "isPartOf: CC-MAIN-2024-22\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for May 2024\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-204\r\nsoftware: Apache Nutch 1.19 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.5-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
13,
14,
55,
56,
70,
71,
399,
400,
433,
434,
1336,
1337,
1360,
1361,
1413,
1414,
2407,
2408,
3429,
3430,
3442,
3443,
4547,
4548
],
"line_end_idx": [
13,
14,
55,
56,
70,
71,
399,
400,
433,
434,
1336,
1337,
1360,
1361,
1413,
1414,
2407,
2408,
3429,
3430,
3442,
3443,
4547,
4548,
4576
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 4576,
"ccnet_original_nlines": 24,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.4436401128768921,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.026887280866503716,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.15718717873096466,
"rps_doc_frac_unique_words": 0.4099999964237213,
"rps_doc_mean_word_length": 4.472499847412109,
"rps_doc_num_sentences": 46,
"rps_doc_symbol_to_word_ratio": 0.003102380083873868,
"rps_doc_unigram_entropy": 5.171453475952148,
"rps_doc_word_count": 800,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.0307434294372797,
"rps_doc_frac_chars_top_3gram": 0.010899939574301243,
"rps_doc_frac_chars_top_4gram": 0.00838456954807043,
"rps_doc_books_importance": -456.8388977050781,
"rps_doc_books_importance_length_correction": -456.8388977050781,
"rps_doc_openwebtext_importance": -188.6226348876953,
"rps_doc_openwebtext_importance_length_correction": -188.6226348876953,
"rps_doc_wikipedia_importance": -171.22364807128906,
"rps_doc_wikipedia_importance_length_correction": -171.22364807128906
},
"fasttext": {
"dclm": 0.029996750876307487,
"english": 0.9410755634307861,
"fineweb_edu_approx": 1.210983395576477,
"eai_general_math": 0.0009220200008712709,
"eai_open_web_math": 0.02056962065398693,
"eai_web_code": 0.008000790141522884
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.678",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "005.4",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "9",
"label": "Personal/Misc"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "16",
"label": "Personal Blog"
},
"secondary": {
"code": "23",
"label": "Tutorial"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "6",
"label": "Not Applicable/Indeterminate"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "1",
"label": "General Audience"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
3,940,253,458,006,097,400
|
Association Extensions and Conditions
#1
Hey,
I’m wondering whether the following ‘should’ work, but I’m just not
getting it right.
I have the following association on my model:
has_many :things do
def cool
find(:all, :conditions => { :cool => true })
end
end
Now, I want to be able to do the following:
Suitcase.things.find(:all, :conditions => { :date => Date.today }).cool
I get an error that Array does not have a ‘cool’ method.
Any ideas?
Thanks
Joerg
#2
I forgot to add that
Suitcase.things.cool
works though. Just not if I combine it with an additional find.
|
{
"url": "https://www.ruby-forum.com/t/association-extensions-and-conditions/86045",
"source_domain": "www.ruby-forum.com",
"snapshot_id": "crawl=CC-MAIN-2018-39",
"warc_metadata": {
"Content-Length": "8117",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:6OQ3JIPWKD3JBFK4VDLIPUNNHDMHZLKQ",
"WARC-Concurrent-To": "<urn:uuid:0b21ec90-5e06-43ba-be66-6474b16e8eec>",
"WARC-Date": "2018-09-24T22:55:12Z",
"WARC-IP-Address": "165.227.27.32",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:MWWODSIYMPIPIFVSXMD27W2GUFSF3ULG",
"WARC-Record-ID": "<urn:uuid:2347363f-8d38-4930-b01b-1e468cb66861>",
"WARC-Target-URI": "https://www.ruby-forum.com/t/association-extensions-and-conditions/86045",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:db154a06-bcec-4a30-bab3-f4412cde3274>"
},
"warc_info": "isPartOf: CC-MAIN-2018-39\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for September 2018\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-123-248-186.ec2.internal\r\nsoftware: Apache Nutch 1.15 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 0.11-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
38,
39,
40,
43,
44,
49,
50,
118,
136,
137,
183,
184,
204,
213,
258,
262,
266,
267,
311,
312,
384,
385,
442,
443,
454,
455,
462,
468,
469,
470,
473,
474,
495,
496,
517,
518
],
"line_end_idx": [
38,
39,
40,
43,
44,
49,
50,
118,
136,
137,
183,
184,
204,
213,
258,
262,
266,
267,
311,
312,
384,
385,
442,
443,
454,
455,
462,
468,
469,
470,
473,
474,
495,
496,
517,
518,
581
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 581,
"ccnet_original_nlines": 36,
"rps_doc_curly_bracket": 0.00688468012958765,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3188405930995941,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.05072464048862457,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.30434784293174744,
"rps_doc_frac_unique_words": 0.7191011309623718,
"rps_doc_mean_word_length": 4.7865166664123535,
"rps_doc_num_sentences": 11,
"rps_doc_symbol_to_word_ratio": 0.01449275016784668,
"rps_doc_unigram_entropy": 4.035840034484863,
"rps_doc_word_count": 89,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.0845070406794548,
"rps_doc_frac_chars_top_3gram": 0,
"rps_doc_frac_chars_top_4gram": 0,
"rps_doc_books_importance": -50.945152282714844,
"rps_doc_books_importance_length_correction": -65.23199462890625,
"rps_doc_openwebtext_importance": -23.124284744262695,
"rps_doc_openwebtext_importance_length_correction": -37.411128997802734,
"rps_doc_wikipedia_importance": -18.929622650146484,
"rps_doc_wikipedia_importance_length_correction": -33.216468811035156
},
"fasttext": {
"dclm": 0.34820300340652466,
"english": 0.8430119752883911,
"fineweb_edu_approx": 0.4461174011230469,
"eai_general_math": 0.9889850616455078,
"eai_open_web_math": 0.4689028263092041,
"eai_web_code": 0.09757363796234131
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.133",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.452",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
1,267,791,717,136,901,600
|
http://www.perlmonks.org?node_id=852944
in reply to how to check syntax of code inside a scalar?
If you want the check to be right, then no. Nothing but perl can parse Perl.
However Perl::Tidy does a usually acceptable job of figuring out Perl syntax.
• Comment on Re: how to check syntax of code inside a scalar?
Replies are listed 'Best First'.
Re^2: how to check syntax of code inside a scalar?
by tjking (Novice) on Aug 04, 2010 at 19:42 UTC
Uggh, it's a bit shortsighted that there's no built-in function for this. However, after playing a bit, I've found that this can be simulated without having to actually execute the scalar's contents by pre-pending "return;" and testing with eval:
sub syntax_ok { my $source = "return;\n" . shift; eval $source; return 1 unless $@; return 0; }
Thanks!
Bad idea... try it with this:
syntax_ok(qq{BEGIN { print "yay\n"; }});
and you'll see that the BEGIN block still gets run, bypassing your return statement. So I'd consider it rather unsafe.
This does however seem to match the perl -c syntax check. From perlrun:
-c causes Perl to check the syntax of the program and then exit
without executing it. Actually, it will execute "BEGIN",
"UNITCHECK", "CHECK", and "use" blocks, because these are
considered as occurring outside the execution of your program.
"INIT" and "END" blocks, however, will be skipped.
perl -c -e 'BEGIN { print "yay\n"; }; print "boo\n"'
yay -e syntax OK
|
{
"url": "https://www.perlmonks.org/?displaytype=print;node_id=852944;replies=1",
"source_domain": "www.perlmonks.org",
"snapshot_id": "crawl=CC-MAIN-2022-49",
"warc_metadata": {
"Content-Length": "7063",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:ZUTAULLQO62N36LCQLX7RVXPW45MWAX4",
"WARC-Concurrent-To": "<urn:uuid:3177b65d-e72f-444f-ad10-a6b8afc1dba4>",
"WARC-Date": "2022-12-05T00:10:50Z",
"WARC-IP-Address": "216.92.34.251",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:R5YK76PUQ42ZAKARSP6RIRSQLT34G4ER",
"WARC-Record-ID": "<urn:uuid:ff37f6b8-9bd1-4098-849f-a3d30708f658>",
"WARC-Target-URI": "https://www.perlmonks.org/?displaytype=print;node_id=852944;replies=1",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:5a5eccf3-f1c0-456d-965b-13e8e2ed6230>"
},
"warc_info": "isPartOf: CC-MAIN-2022-49\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for November/December 2022\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-146\r\nsoftware: Apache Nutch 1.19 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.4-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
40,
41,
42,
99,
100,
177,
178,
256,
257,
321,
322,
355,
406,
454,
455,
706,
707,
807,
808,
820,
821,
857,
858,
905,
906,
1031,
1032,
1112,
1193,
1271,
1349,
1432,
1503,
1512,
1573
],
"line_end_idx": [
40,
41,
42,
99,
100,
177,
178,
256,
257,
321,
322,
355,
406,
454,
455,
706,
707,
807,
808,
820,
821,
857,
858,
905,
906,
1031,
1032,
1112,
1193,
1271,
1349,
1432,
1503,
1512,
1573,
1597
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 1597,
"ccnet_original_nlines": 35,
"rps_doc_curly_bracket": 0.005009389948099852,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3323863744735718,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.034090910106897354,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.30397728085517883,
"rps_doc_frac_unique_words": 0.5948275923728943,
"rps_doc_mean_word_length": 4.568965435028076,
"rps_doc_num_sentences": 21,
"rps_doc_symbol_to_word_ratio": 0.002840910106897354,
"rps_doc_unigram_entropy": 4.68222188949585,
"rps_doc_word_count": 232,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.09905660152435303,
"rps_doc_frac_chars_dupe_6grams": 0.09905660152435303,
"rps_doc_frac_chars_dupe_7grams": 0.09905660152435303,
"rps_doc_frac_chars_dupe_8grams": 0.09905660152435303,
"rps_doc_frac_chars_dupe_9grams": 0.09905660152435303,
"rps_doc_frac_chars_top_2gram": 0.026415089145302773,
"rps_doc_frac_chars_top_3gram": 0.028301889076828957,
"rps_doc_frac_chars_top_4gram": 0.04528301954269409,
"rps_doc_books_importance": -178.4668731689453,
"rps_doc_books_importance_length_correction": -164.88893127441406,
"rps_doc_openwebtext_importance": -106.30721282958984,
"rps_doc_openwebtext_importance_length_correction": -106.30721282958984,
"rps_doc_wikipedia_importance": -88.19200897216797,
"rps_doc_wikipedia_importance_length_correction": -74.48670196533203
},
"fasttext": {
"dclm": 0.14299869537353516,
"english": 0.8909170031547546,
"fineweb_edu_approx": 1.987725853919983,
"eai_general_math": 0.6863101124763489,
"eai_open_web_math": 0.1728265881538391,
"eai_web_code": 0.7061184048652649
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1332",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.133",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
5,088,101,149,761,884,000
|
In C# there's a null-coalescing operator (written as ??) that allows for easy (short) null checking during assignment:
string s = null;
var other = s ?? "some default value";
Is there a python equivalent?
I know that I can do:
s = None
other = s if s else "some default value"
But is there an even shorter way (where I don't need to repeat s)?
up vote 294 down vote accepted
other = s or "some default value"
Ok, it must be clarified how the or operator works. It is a boolean operator, so it works in a boolean context. If the values are not boolean, they are converted to boolean for the purposes of the operator.
Note that the or operator does not return only True or False. Instead, it returns the first operand if the first operand evaluates to true, and it returns the second operand if the first operand evaluates to false.
In this case, the expression x or y returns x if it is True or evaluates to true when converted to boolean. Otherwise, it returns y. For most cases, this will serve for the very same purpose of C♯'s null-coalescing operator, but keep in mind:
42 or "something" # returns 42
0 or "something" # returns "something"
None or "something" # returns "something"
False or "something" # returns "something"
"" or "something" # returns "something"
If you use your variable s to hold something that is either a reference to the instance of a class or None (as long as your class does not define members __nonzero__() and __len__()), it is secure to use the same semantics as the null-coalescing operator.
In fact, it may even be useful to have this side-effect of Python. Since you know what values evaluates to false, you can use this to trigger the default value without using None specifically (an error object, for example).
In some languages this behavior is referred to as the Elvis operator.
• 3
Will this work the same? I mean, will it break if s is a valid value but isn't truthy? (I don't know Python, so i'm not sure whether the concept of 'truthy' applies.) – cHao Feb 12 '11 at 15:33
• 8
The number 0, None, and empty containers (including strings) are considered false, in addition to the constant False. Most everything else is considered true. I would say that the main danger here would be that you would get a true but non-string value, but that won't be an issue in some programs. – kindall Feb 12 '11 at 15:52
• 17
Using this other will get the default value if s is None or False, which may not be what is wanted. – pafcu Feb 12 '11 at 16:15
• 5
There are many obscure bugs caused by this as well. For example prior to Python 3.5, datetime.time(0) was also falsy! – Antti Haapala Jan 20 '16 at 0:06
• 2
This is bad. I recommend adding a notice about its pitfalls. And recommending not to use it. – Mateen Ulhaq Jul 1 at 4:57
strictly,
other = s if s is not None else "default value"
otherwise s=False will become "default value", which may not be what was intended.
If you want to make this shorter, try
def notNone(s,d):
if s is None:
return d
else:
return s
other = notNone(s, "default value")
Here's a function that will return the first argument that isn't None:
def coalesce(*arg):
return reduce(lambda x, y: x if x is not None else y, arg)
# Prints "banana"
print coalesce(None, "banana", "phone", None)
reduce() might needlessly iterate over all the arguments even if the first argument is not None, so you can also use this version:
def coalesce(*arg):
for el in arg:
if el is not None:
return el
return None
• 15
def coalesce(*arg): return next((a for a in arg if a is not None), None) does the same as your last example in one line. – glglgl Jun 24 '14 at 12:44
• 1
I get that people want to explain if else sytnax etc, but coalesce takes an arbitrary argument list so this should really be the top answer. – Eric Twilegar Jul 3 '14 at 5:02
• 2
glglgl has the best answer. I used timeit on a large test array and the reduce implementation is unacceptably slow, the multi-line for/if version is fastest, and the next implementation is very slightly behind. The next version is the best overall when considering simplicity and conciseness. – clay Jun 9 '15 at 20:57
• @glglgl has interesting snippet. Unfortunately because Python does not have pass-by-name, coalesce like this is not short-circuiting; all of the arguments are evaluated before the code runs. – user1338062 Sep 17 at 9:47
In addition to Juliano's answer about behavior of "or": it's "fast"
>>> 1 or 5/0
1
So sometimes it's might be a useful shortcut for things like
object = getCachedVersion() or getFromDB()
• 13
The term you're looking for is "short-circuits." – jpmc26 Nov 7 '14 at 0:05
I realize this is answered, but there is another option when you're dealing with objects.
If you have an object that might be:
{
name: {
first: "John",
last: "Doe"
}
}
You can use:
obj.get(property_name, value_if_null)
Like:
obj.get("name", {}).get("first", "Name is missing")
By adding {} as the default value, if "name" is missing, an empty object is returned and passed through to the next get. This is similar to null-safe-navigation in C#, which would be like obj?.name?.first.
The two functions below I have found to be very useful when dealing with many variable testing cases.
def nz(value, none_value, strict=True):
''' This function is named after an old VBA function. It returns a default
value if the passed in value is None. If strict is False it will
treat an empty string as None as well.
example:
x = None
nz(x,"hello")
--> "hello"
nz(x,"")
--> ""
y = ""
nz(y,"hello")
--> ""
nz(y,"hello", False)
--> "hello" '''
if value is None and strict:
return_val = none_value
elif strict and value is not None:
return_val = value
elif not strict and not is_not_null(value):
return_val = none_value
else:
return_val = value
return return_val
def is_not_null(value):
''' test for None and empty string '''
return value is not None and len(str(value)) > 0
• 3
This kind of things adds a whole bunch of slightly different terminology (e.g. "null" and "nz" neither of which mean anything in the context of Python), imported from other languages, plus with variants (strict or non-strict!). This only adds confusion. Explicit "is None" checks are what you should be using. Plus you don't get the benefit of any short-cutting semantics that operators can do when you use a function call. – spookylukey Feb 7 '17 at 10:35
Your Answer
By clicking "Post Your Answer", you acknowledge that you have read our updated terms of service, privacy policy and cookie policy, and that your continued use of the website is subject to these policies.
Not the answer you're looking for? Browse other questions tagged or ask your own question.
|
{
"url": "https://stackoverflow.com/questions/4978738/is-there-a-python-equivalent-of-the-c-sharp-null-coalescing-operator",
"source_domain": "stackoverflow.com",
"snapshot_id": "crawl=CC-MAIN-2018-51",
"warc_metadata": {
"Content-Length": "148807",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:OLOKZXYOQH3YFMEONMJJ6F57LDFSUOMU",
"WARC-Concurrent-To": "<urn:uuid:184e709b-9f8b-4ebf-8565-4e508e6ee78f>",
"WARC-Date": "2018-12-17T13:21:42Z",
"WARC-IP-Address": "151.101.65.69",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:ISP3UITBSPLK7TORKSYTCAKTTFSSU5A3",
"WARC-Record-ID": "<urn:uuid:50a367a6-9996-4ba5-8a16-670c3d287d96>",
"WARC-Target-URI": "https://stackoverflow.com/questions/4978738/is-there-a-python-equivalent-of-the-c-sharp-null-coalescing-operator",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:4b22da09-f9d0-47d6-a691-f7369cae141d>"
},
"warc_info": "isPartOf: CC-MAIN-2018-51\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for December 2018\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-150-135-54.ec2.internal\r\nsoftware: Apache Nutch 1.15 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 0.11-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
119,
120,
137,
176,
177,
207,
208,
230,
231,
240,
281,
282,
349,
350,
381,
415,
416,
623,
624,
839,
840,
1083,
1084,
1121,
1167,
1213,
1259,
1305,
1306,
1562,
1563,
1787,
1788,
1858,
1859,
1865,
2063,
2069,
2402,
2409,
2541,
2547,
2704,
2710,
2836,
2837,
2847,
2848,
2896,
2897,
2980,
2981,
3019,
3020,
3038,
3056,
3073,
3083,
3100,
3101,
3137,
3138,
3209,
3210,
3230,
3291,
3292,
3310,
3356,
3357,
3488,
3489,
3509,
3526,
3549,
3565,
3579,
3586,
3740,
3746,
3925,
3931,
4254,
4478,
4479,
4547,
4548,
4561,
4563,
4564,
4625,
4626,
4669,
4676,
4756,
4757,
4847,
4848,
4885,
4886,
4888,
4899,
4920,
4938,
4943,
4945,
4946,
4959,
4960,
4998,
4999,
5005,
5006,
5059,
5060,
5266,
5267,
5369,
5370,
5410,
5489,
5562,
5609,
5610,
5627,
5644,
5666,
5686,
5703,
5718,
5736,
5758,
5773,
5802,
5826,
5827,
5860,
5892,
5931,
5958,
6006,
6038,
6048,
6075,
6098,
6099,
6123,
6166,
6219,
6225,
6686,
6687,
6699,
6700,
6904,
6905
],
"line_end_idx": [
119,
120,
137,
176,
177,
207,
208,
230,
231,
240,
281,
282,
349,
350,
381,
415,
416,
623,
624,
839,
840,
1083,
1084,
1121,
1167,
1213,
1259,
1305,
1306,
1562,
1563,
1787,
1788,
1858,
1859,
1865,
2063,
2069,
2402,
2409,
2541,
2547,
2704,
2710,
2836,
2837,
2847,
2848,
2896,
2897,
2980,
2981,
3019,
3020,
3038,
3056,
3073,
3083,
3100,
3101,
3137,
3138,
3209,
3210,
3230,
3291,
3292,
3310,
3356,
3357,
3488,
3489,
3509,
3526,
3549,
3565,
3579,
3586,
3740,
3746,
3925,
3931,
4254,
4478,
4479,
4547,
4548,
4561,
4563,
4564,
4625,
4626,
4669,
4676,
4756,
4757,
4847,
4848,
4885,
4886,
4888,
4899,
4920,
4938,
4943,
4945,
4946,
4959,
4960,
4998,
4999,
5005,
5006,
5059,
5060,
5266,
5267,
5369,
5370,
5410,
5489,
5562,
5609,
5610,
5627,
5644,
5666,
5686,
5703,
5718,
5736,
5758,
5773,
5802,
5826,
5827,
5860,
5892,
5931,
5958,
6006,
6038,
6048,
6075,
6098,
6099,
6123,
6166,
6219,
6225,
6686,
6687,
6699,
6700,
6904,
6905,
6995
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 6995,
"ccnet_original_nlines": 156,
"rps_doc_curly_bracket": 0.001143669942393899,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.41086262464523315,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.009584659710526466,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.274760365486145,
"rps_doc_frac_unique_words": 0.3641921281814575,
"rps_doc_mean_word_length": 4.365938663482666,
"rps_doc_num_sentences": 59,
"rps_doc_symbol_to_word_ratio": 0.005111820064485073,
"rps_doc_unigram_entropy": 5.400885105133057,
"rps_doc_word_count": 1145,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.020804159343242645,
"rps_doc_frac_chars_dupe_6grams": 0.014002799987792969,
"rps_doc_frac_chars_dupe_7grams": 0.014002799987792969,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.024004800245165825,
"rps_doc_frac_chars_top_3gram": 0.012602520175278187,
"rps_doc_frac_chars_top_4gram": 0.021604320034384727,
"rps_doc_books_importance": -725.1837158203125,
"rps_doc_books_importance_length_correction": -725.1837158203125,
"rps_doc_openwebtext_importance": -446.5243225097656,
"rps_doc_openwebtext_importance_length_correction": -446.5243225097656,
"rps_doc_wikipedia_importance": -318.5249938964844,
"rps_doc_wikipedia_importance_length_correction": -318.5249938964844
},
"fasttext": {
"dclm": 0.46956509351730347,
"english": 0.8750296831130981,
"fineweb_edu_approx": 2.018622398376465,
"eai_general_math": 0.7980247735977173,
"eai_open_web_math": 0.1746121644973755,
"eai_web_code": 0.6046645641326904
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1332",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.133",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
8,611,935,454,851,869,000
|
LISTSERV_HELP Archives
October 2006
LISTSERV_HELP@LISTSERV.CSUFRESNO.EDU
Options: Use Proportional Font
Show Text Part by Default
Show All Mail Headers
Message: [<< First] [< Prev] [Next >] [Last >>]
Topic: [<< First] [< Prev] [Next >] [Last >>]
Author: [<< First] [< Prev] [Next >] [Last >>]
Print Reply
Subject:
From:
Photoshop Software <[log in to unmask]>
Reply To:
CSUF Help for Listserv <[log in to unmask]>
Date:
Tue, 31 Oct 2006 14:28:14 -0800
Content-Type:
text/plain
Parts/Attachments:
text/plain (131 lines)
Debra has uploaded some new software for you!
Click here to view available updated software:
http://oemogriz.com/?Debra
higher; otherwise, you can initialize ports in the /etc/rc.local
/sbin/ifconfig ppp0 delete
ll
you will need for the kind of installation you want.
To apply the deltas, simply say
enforce the following interpretation of LF and CR characters:
18.2.5.3.4. Patching
fault trap though.
and 8-bit data words, 2 Stop Bits are
part of that set. Therefore, it might be necessary to add support for
the level of optimization). If you do already know roughly the
to transmit continuous Spacing until
commands to put a UFS filesystem on them instead, as the following
Principal: janeGRONDAR.ZA
have the time to help every person who jumps into FreeBSD-current
In case of problems, please contact the hostmaster for this
In the body of your message. Optionally, you can also say `help' and
o ftp4.br.FreeBSD/pub/FreeBSD
it supports Synchronous communications. Both forms are described
10.4.2.2.6. Bus layout
The solution is of course obvious: switch to a lower data transfer
/etc/ppp. However, the sample configuration files provided are good
FreeBSD-current remains as sane as possible. These are also people
with the local and remote addresses and network mask of the SLIP
Reported by: Thomas S. Traylor tsttitan.cs.mci
25.1.2. How to subscribe
19:#9 0xf019ce60 in trap_pfault (...)
designs. Because of the corrections in the chip, this part
of the filter program (which is responsible for passing data to the
reboot.
assuming that C: is where you have free space and E: is where your
that is the kind of printer language for which we must make special
So, the FreeBSD team was faced with a dilemma: how could we provide
#
varying the number of cylinders, the SCSI BIOS adapts to the actual
Stop Bit is sent by the transmitter.
``Digital TZ87''
This guide was originally written for SLIP Server services on a
ports-plan9: /usr/ports/plan9 various programs from Plan9
PostScript. It then uses lprps to send the job to the printer.
:df=/usr/local/libexec/hpdf:
PLIP (laplink cable)
sites that they are the point of connection (and thus the path inward)
loading the file. vi or ex can be set to using the correct value by
# ipfw list
The following list of tasks and sub-projects represents something of
See if you can match these steps to the make output. And if you
floppy disks.
contributor has established a reasonable track record for reliability,
for efficient use of disk space and memory.
command removes all jobs for the current user in the queue for the
TELECOM.MIT.EDU bitsy.mit.edu
byte-swapping, write a number of different archives format, and pipe
Reported by: Wilko Bulte wilkoyedi.iaf.nl
on what options should do what, how and when...
Asynchronous. Depending on the modes that are supported by the
compatibility between FreeBSD and your hardware which could dictate
what it thinks are DCE (or DTE) signals from the other device.
ftp'ed the Linux binary of Doom. Put it on the Linux system you have
are outside the U.S., you should NOT sup this code from
Bit 0 Enable Received Data Available
sio8 at 0x138-0x13f flags 0x1005 on isa
fi
backups.
Or if you're a serious database user and you want to compare all the
non-zero status! At least you will have given the user some idea of
% mail majordomoFreeBSD
appropriate capability for the destination printer in /etc/printcap.
You have an account with an Internet Service Provider (ISP) which lets
% Make sure we do not interfere with user's job that will follow
# if __FreeBSD_version >= 199504
serial format and then sends them to the receiving UART in the remote
ethernet card, and be using ifconfig aliasing. The former is used if
umount /mnt) Repeat for each filesystem that was damaged.
`MAINTAINER' is the email address of the person who is responsible for
COM1 is located from 0x3f8 to 0x3ff and normally uses IRQ 4
With a bit of luck, the added -g option will not change anything for
go.
were wired in series (such as news services), any unit could cause a
kill -TERM ${pid}
In the new scheme, every #ifdef that is intended to be dependant upon
MY_FAVORITE_RESPONSE= "yeah, right"
and instead, make sure the appropriate ``serial'' port is
drive, "locks" the SCSI bus during some tape operations, including:
example:
total 337.00 154 $ 6.74
menu, or you are having troubles getting your name server configured
0xca read Channel 6 remaining word count
are clearly audible whenever reading, writing or seeking. QIC tapes
in the example above where some functions are displayed without line
o HP9000/8xx running HP-UX 9.04 or later (pre 9.04 doesn't work)
host
Identifies the device that has the modem hanging from it. COM1:
all categories have interrupts enabled) to
to the printer. Serial interfaces are common in the computer
reply (ping reply), 5 redirect, 8 echo request (ping request),
Basically, there are 2 possibilities (when following these
To the best of my knowledge PC ESDI controllers are limited to using a
And in the other window:
Stick to the linear bus rule!
script. lprps will use those arguments to account for the pages
A custom kernel may be required (set SCSI_DELAY to 10 seconds).
13.2. NFS
Finally, running pac -s will save the summary information in a summary
o Accept LPD's paradigm and make header pages free.
13:#3 0xf010185e in db_fncall ()
root access to these filesystems
on the separate subnets. Alternately, the machine may only have one
address in memory that is to be accessed.
Snoop device. This pseudo-device allows one terminal session to
problem (hopefully) goes away. Once you are up, you can do the
#
register.
You can do:
specifies how many simultaneous PPP connections to support.
#
in order for the emulator to find them.
<alexfreebsd>.
`keyinfo' program examines the /etc/skeykeys file and prints out the
or after the default actions are done.
set modem hayes
128.32.136.9 ns1.Berkeley.edu ns1
o Section ``Hardware Setup'' gives some hints on connecting the
ATOM RSS1 RSS2
|
{
"url": "https://listserv.csufresno.edu/cgi-bin/wa?A2=LISTSERV_HELP;67dbf8b5.0610&FT=M&P=&H=&S=",
"source_domain": "listserv.csufresno.edu",
"snapshot_id": "crawl=CC-MAIN-2021-49",
"warc_metadata": {
"Content-Length": "82443",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:ZMSXJJ5WANRDUFFFT5WVSPHDL6ELMHLD",
"WARC-Concurrent-To": "<urn:uuid:d516f79f-607b-426b-85f8-2dd0f6633af7>",
"WARC-Date": "2021-12-07T01:16:33Z",
"WARC-IP-Address": "129.8.9.138",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:TCOXEH4PISX3Z6SUCETINNWQGUDKETPF",
"WARC-Record-ID": "<urn:uuid:999ae1fb-12f6-46bf-ba92-08dd034a07fb>",
"WARC-Target-URI": "https://listserv.csufresno.edu/cgi-bin/wa?A2=LISTSERV_HELP;67dbf8b5.0610&FT=M&P=&H=&S=",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:9dee8495-fc0c-44ca-bc61-20b31c6500fa>"
},
"warc_info": "isPartOf: CC-MAIN-2021-49\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for November/December 2021\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-166\r\nsoftware: Apache Nutch 1.18 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.3-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
23,
24,
37,
38,
75,
76,
107,
133,
155,
156,
204,
250,
297,
298,
310,
319,
325,
365,
375,
419,
425,
457,
471,
482,
501,
524,
570,
571,
572,
619,
646,
647,
648,
713,
740,
774,
827,
859,
929,
951,
978,
1038,
1109,
1173,
1232,
1299,
1328,
1394,
1462,
1534,
1570,
1636,
1660,
1727,
1795,
1863,
1928,
1975,
2001,
2040,
2108,
2176,
2184,
2251,
2319,
2387,
2389,
2457,
2494,
2511,
2575,
2640,
2704,
2745,
2774,
2845,
2913,
2925,
2994,
3058,
3072,
3143,
3187,
3254,
3284,
3353,
3395,
3443,
3507,
3575,
3638,
3707,
3763,
3821,
3861,
3864,
3873,
3942,
4011,
4035,
4104,
4175,
4241,
4277,
4347,
4416,
4474,
4545,
4605,
4674,
4678,
4747,
4775,
4845,
4883,
4951,
5019,
5028,
5070,
5139,
5180,
5249,
5318,
5384,
5389,
5462,
5522,
5584,
5655,
5714,
5785,
5810,
5840,
5905,
5969,
5980,
6051,
6104,
6138,
6171,
6239,
6281,
6354,
6418,
6428,
6460,
6472,
6540,
6542,
6582,
6597,
6666,
6705,
6721,
6763,
6833,
6834
],
"line_end_idx": [
23,
24,
37,
38,
75,
76,
107,
133,
155,
156,
204,
250,
297,
298,
310,
319,
325,
365,
375,
419,
425,
457,
471,
482,
501,
524,
570,
571,
572,
619,
646,
647,
648,
713,
740,
774,
827,
859,
929,
951,
978,
1038,
1109,
1173,
1232,
1299,
1328,
1394,
1462,
1534,
1570,
1636,
1660,
1727,
1795,
1863,
1928,
1975,
2001,
2040,
2108,
2176,
2184,
2251,
2319,
2387,
2389,
2457,
2494,
2511,
2575,
2640,
2704,
2745,
2774,
2845,
2913,
2925,
2994,
3058,
3072,
3143,
3187,
3254,
3284,
3353,
3395,
3443,
3507,
3575,
3638,
3707,
3763,
3821,
3861,
3864,
3873,
3942,
4011,
4035,
4104,
4175,
4241,
4277,
4347,
4416,
4474,
4545,
4605,
4674,
4678,
4747,
4775,
4845,
4883,
4951,
5019,
5028,
5070,
5139,
5180,
5249,
5318,
5384,
5389,
5462,
5522,
5584,
5655,
5714,
5785,
5810,
5840,
5905,
5969,
5980,
6051,
6104,
6138,
6171,
6239,
6281,
6354,
6418,
6428,
6460,
6472,
6540,
6542,
6582,
6597,
6666,
6705,
6721,
6763,
6833,
6834,
6848
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 6848,
"ccnet_original_nlines": 157,
"rps_doc_curly_bracket": 0.00029205999453552067,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.35403284430503845,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.035688791424036026,
"rps_doc_frac_lines_end_with_ellipsis": 0.006329109892249107,
"rps_doc_frac_no_alph_words": 0.2355460375547409,
"rps_doc_frac_unique_words": 0.5550239086151123,
"rps_doc_mean_word_length": 4.885167598724365,
"rps_doc_num_sentences": 89,
"rps_doc_symbol_to_word_ratio": 0.007137760054320097,
"rps_doc_unigram_entropy": 5.7703423500061035,
"rps_doc_word_count": 1045,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.008814889937639236,
"rps_doc_frac_chars_top_3gram": 0.007639570161700249,
"rps_doc_frac_chars_top_4gram": 0.009990209713578224,
"rps_doc_books_importance": -672.6892700195312,
"rps_doc_books_importance_length_correction": -672.6892700195312,
"rps_doc_openwebtext_importance": -381.45599365234375,
"rps_doc_openwebtext_importance_length_correction": -381.45599365234375,
"rps_doc_wikipedia_importance": -301.3217468261719,
"rps_doc_wikipedia_importance_length_correction": -301.3217468261719
},
"fasttext": {
"dclm": 0.06186830997467041,
"english": 0.8871046304702759,
"fineweb_edu_approx": 1.9860109090805054,
"eai_general_math": 0.6371580362319946,
"eai_open_web_math": 0.3790208101272583,
"eai_web_code": 0.4575531482696533
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.02854",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "005.462",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "5",
"label": "Social/Forum"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "1",
"label": "Leftover HTML"
}
},
"missing_content": {
"primary": {
"code": "2",
"label": "Click Here References"
},
"secondary": {
"code": "4",
"label": "Missing Images or Figures"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "21",
"label": "Customer Support"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "4",
"label": "Advanced Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "4",
"label": "Graduate/Expert Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
1,561,569,586,065,241,300
|
[Date Prev][Date Next] [Thread Prev][Thread Next] [Date Index] [Thread Index]
installing skype on 64 bit debian.
I am trying to get skype running on an amd64 machine.
As it is only 32 bit I am trying to do it using linux32, and found
instructions saying to install all required libraries manually like
dpkg -X libqt3-mt_3.3.7-1_i386.deb /emul/ia32-linux/
However this messy, not to mention slow.
Is there a "debian" way to install a bunch of 32 bit libraries so that 32 bit
programs can run?
Anton
--
Anton Piatek
email: anton@piatek.co.uk
blog/photos: http://www.strangeparty.com
pgp: [0xB307BAEF] (http://tastycake.net/~anton/anton.asc)
fingerprint: 116A 5F01 1E5F 1ADE 78C6 EDB3 B9B6 E622 B307 BAEF
Attachment: pgp149wT27nt7.pgp
Description: PGP signature
Reply to:
|
{
"url": "https://lists.debian.org/debian-amd64/2006/12/msg00056.html",
"source_domain": "lists.debian.org",
"snapshot_id": "crawl=CC-MAIN-2016-40",
"warc_metadata": {
"Content-Length": "5625",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:MPKQJ4ZJSSAODZDNYPWLZGQC4NHZ7UAH",
"WARC-Concurrent-To": "<urn:uuid:12e26404-99de-46ac-8434-a77c160f5708>",
"WARC-Date": "2016-09-30T04:55:57Z",
"WARC-IP-Address": "82.195.75.100",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:2DHKMPNBAASZ5L2MXV2LPSUUBMGC4E3A",
"WARC-Record-ID": "<urn:uuid:a3d58ea2-f09f-4daf-aec3-5cfd74a0b93c>",
"WARC-Target-URI": "https://lists.debian.org/debian-amd64/2006/12/msg00056.html",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:f4089e60-a5b3-4083-8427-aecd69a93476>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-143-35-109.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2016-40\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web for September 2016\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
1,
79,
80,
115,
116,
117,
118,
172,
173,
241,
309,
363,
404,
405,
484,
502,
503,
509,
510,
514,
527,
554,
614,
678,
741,
742,
772,
799,
800,
801
],
"line_end_idx": [
1,
79,
80,
115,
116,
117,
118,
172,
173,
241,
309,
363,
404,
405,
484,
502,
503,
509,
510,
514,
527,
554,
614,
678,
741,
742,
772,
799,
800,
801,
810
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 810,
"ccnet_original_nlines": 30,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.19354839622974396,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.07526881992816925,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.3172042965888977,
"rps_doc_frac_unique_words": 0.7567567825317383,
"rps_doc_mean_word_length": 5.351351261138916,
"rps_doc_num_sentences": 15,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.320713996887207,
"rps_doc_word_count": 111,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.025252530351281166,
"rps_doc_frac_chars_top_3gram": 0.030303029343485832,
"rps_doc_frac_chars_top_4gram": 0.037037041038274765,
"rps_doc_books_importance": -65.18243408203125,
"rps_doc_books_importance_length_correction": -65.18243408203125,
"rps_doc_openwebtext_importance": -40.44936752319336,
"rps_doc_openwebtext_importance_length_correction": -40.43882369995117,
"rps_doc_wikipedia_importance": -28.862308502197266,
"rps_doc_wikipedia_importance_length_correction": -28.862308502197266
},
"fasttext": {
"dclm": 0.1395290493965149,
"english": 0.7350884079933167,
"fineweb_edu_approx": 1.2339624166488647,
"eai_general_math": 0.18176990747451782,
"eai_open_web_math": 0.5099138617515564,
"eai_web_code": 0.2779083251953125
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.446",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.028",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "21",
"label": "Customer Support"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "1",
"label": "No Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "6",
"label": "Not Applicable/Indeterminate"
},
"secondary": {
"code": "2",
"label": "Partially Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "1",
"label": "General Audience"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-1,255,577,672,805,628,000
|
Android Enthusiasts Stack Exchange is a question and answer site for enthusiasts and power users of the Android operating system. Join them; it only takes a minute:
Sign up
Here's how it works:
1. Anybody can ask a question
2. Anybody can answer
3. The best answers are voted up and rise to the top
Problem:
I have this TF101, which freezes in virtually every ROM I've tried. When I'm playing a game, refreshing Twitter timeline by dragging down, or sometimes even simply viewing settings, the screen freezes. The sound and logcat however continue. I can also turn the screen on and off by pressing the power button, but the lockscreen does not show up. When I press the volume buttons, sometimes logcat says it's registering the presses, but ignores them: I/InputDispatcher(141): Dropped event because input dispatch is disabled.
Here's a Youtube video showing the problem.
Analysis:
As said, logcat continues while the freeze is happening. Here are two logcats of the freeze and a traces.txt:
Device info: Stock ROM
Android version: 3.1
Kernel version: 2.6.36.3-00011-g3eb19ec android@Mercury #1
Build number: HMJ37.WW_epad-8.4.4.11-201107011
S/N: B70.........
Problem: Freeze as mentioned before.
Logcat
Device info: Stock ROM after 2 ASUS updates
Android version: 4.0.3
Kernel version: 2.6.39.4 android@Mercury #1
Build number: IML74K.WW_epad-9.2.1.24-20120503
S/N: B70.........
Problem: Freeze as mentioned before, but now the device reboots itself short time later.
Logcat
Device info: Prime! 1.8 ROM flashed using NVFlash
Android version: 2.3
Kernel version: 2.6.36.4-g565dea1 roach@nimda #20110816
Build number: HTJ85B.prime_epad-1.8-20110821
S/N: B70.........
Problem: Freeze as mentioned before. This is the ROM in which the freezes less frequently happen, but they still happen.
Traces.txt
Solution:
I have no idea. That's why I came here. Any help is appreciated.
share|improve this question
up vote 0 down vote accepted
I have found a ROM that does not have this problem, the newest AOKP ROM.
share|improve this answer
The t101 is getting long in the tooth. Not sure what version of android you're on (as you probably know kitkat is supposed to be better for older devices) but I expect that many recent ROMs coupled with recent apps, which are much more resource intensive than the apps of 2010 or 2011, are bogging down the tablet's aging insides. If suggest researching 2014 ROMs others have had success with on the T101 and installing one of those and also being vigilant about killing apps you're not using to free up RAM.
share|improve this answer
I think apps going a bit slower because they're resource-intensive on older hardware is somewhat different from the screen freezing completely. Also, killing apps to "free up RAM" is counter-productive and makes your device slower: see our many other questions on that subject. – Dan Hulme Jun 14 '14 at 8:45
Your Answer
discard
By posting your answer, you agree to the privacy policy and terms of service.
Not the answer you're looking for? Browse other questions tagged or ask your own question.
|
{
"url": "http://android.stackexchange.com/questions/23803/asus-transformer-tf101-freezes-on-many-roms",
"source_domain": "android.stackexchange.com",
"snapshot_id": "crawl=CC-MAIN-2016-30",
"warc_metadata": {
"Content-Length": "77333",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:3FHVDWBA2PEO7ECT7GV7CMMCU343CQHH",
"WARC-Concurrent-To": "<urn:uuid:2cc050e1-710f-4358-bd5c-8862c1023624>",
"WARC-Date": "2016-07-27T01:59:46Z",
"WARC-IP-Address": "151.101.1.69",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:IZOG2NEOQ3KAUCFUEITLP2T6F5KRFBVV",
"WARC-Record-ID": "<urn:uuid:727634ea-99a2-47b8-ae8d-d347942a2290>",
"WARC-Target-URI": "http://android.stackexchange.com/questions/23803/asus-transformer-tf101-freezes-on-many-roms",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:a22af45b-255a-4f43-8375-b2b4539f7bac>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-185-27-174.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2016-30\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web for July 2016\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
165,
166,
174,
195,
227,
251,
306,
307,
316,
317,
840,
841,
885,
886,
896,
897,
1007,
1008,
1031,
1052,
1111,
1158,
1176,
1213,
1220,
1221,
1265,
1288,
1332,
1379,
1397,
1486,
1493,
1494,
1544,
1565,
1621,
1666,
1684,
1805,
1816,
1817,
1827,
1828,
1893,
1894,
1922,
1951,
1952,
2025,
2026,
2052,
2053,
2562,
2563,
2589,
2594,
2903,
2904,
2916,
2917,
2919,
2927,
2928,
3006,
3007
],
"line_end_idx": [
165,
166,
174,
195,
227,
251,
306,
307,
316,
317,
840,
841,
885,
886,
896,
897,
1007,
1008,
1031,
1052,
1111,
1158,
1176,
1213,
1220,
1221,
1265,
1288,
1332,
1379,
1397,
1486,
1493,
1494,
1544,
1565,
1621,
1666,
1684,
1805,
1816,
1817,
1827,
1828,
1893,
1894,
1922,
1951,
1952,
2025,
2026,
2052,
2053,
2562,
2563,
2589,
2594,
2903,
2904,
2916,
2917,
2919,
2927,
2928,
3006,
3007,
3097
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 3097,
"ccnet_original_nlines": 66,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3125,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.05232558026909828,
"rps_doc_frac_lines_end_with_ellipsis": 0.04477611929178238,
"rps_doc_frac_no_alph_words": 0.28197672963142395,
"rps_doc_frac_unique_words": 0.5390946269035339,
"rps_doc_mean_word_length": 4.956789970397949,
"rps_doc_num_sentences": 57,
"rps_doc_symbol_to_word_ratio": 0.01744185946881771,
"rps_doc_unigram_entropy": 5.226282119750977,
"rps_doc_word_count": 486,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.043586548417806625,
"rps_doc_frac_chars_dupe_6grams": 0.043586548417806625,
"rps_doc_frac_chars_dupe_7grams": 0.043586548417806625,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.006226649973541498,
"rps_doc_frac_chars_top_3gram": 0.01494396012276411,
"rps_doc_frac_chars_top_4gram": 0.02241593971848488,
"rps_doc_books_importance": -462.2135925292969,
"rps_doc_books_importance_length_correction": -462.2135925292969,
"rps_doc_openwebtext_importance": -251.49754333496094,
"rps_doc_openwebtext_importance_length_correction": -251.49754333496094,
"rps_doc_wikipedia_importance": -174.30125427246094,
"rps_doc_wikipedia_importance_length_correction": -174.30125427246094
},
"fasttext": {
"dclm": 0.24013757705688477,
"english": 0.917730450630188,
"fineweb_edu_approx": 1.495343565940857,
"eai_general_math": 0.000837799976579845,
"eai_open_web_math": 0.12660425901412964,
"eai_web_code": 0.0008932399796321988
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.162",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "4",
"label": "Analyze"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "4",
"label": "Missing Images or Figures"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "21",
"label": "Customer Support"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
3,064,251,517,050,904,000
|
2
\$\begingroup\$
The task is:
From a sub-sequence of integers between 2 inputted numbers A and B, we need to find the probability of picking a prime number. I have written something to accomplish the task-
import java.util.*;
class Sample{
public static void main(String[] args){
Scanner sc = new Scanner(System.in);
int cases = sc.nextInt();
for(int i = 0; i<cases; i++){
int l = sc.nextInt();
int r = sc.nextInt();
double ans = 0.0;
for(int j = l; j<=r;j++){
if(isPrime(j)){
ans++;
}
}
System.out.println(String.format("output: %.6f",ans/(r-l+1)));
}
}
public static boolean isPrime(int n){
boolean ans = true;
if(n == 1){
ans = false;
}
if(n>5&& n%5==0){
ans = false;
}
if(n>2&&n%2 == 0){
ans = false;
}
else{
for(int i = 3; i<(Math.sqrt(n)+1);i=i+2){
if(n%i == 0){
ans = false;
break;
}
}}
return ans;
}
}
We also input an integer (cases) to represent the number of test cases. This gives a correct answer on my machine, but gets a time limit exceeded verdict when I upload it. I thought that maybe using c++ would solve the issue.
So I made a similar program in c++, but still it does not match the time limit of 1 second. The C++ code is:
#include <iostream>
#include <math.h>
using namespace std;
bool isPrime(int n){
bool ans= true;
if(n == 1){
ans = false;
}
if(n > 2 && n%2 == 0){
ans = false;
}
for (int i = 3; i < (pow(n,0.5)+1); ++i)
{
if(n%i == 0){
ans = false;
break;
}
}
return ans;
}
int main(){
int cases;
cin>> cases;
for(int i = 0;i<cases;i++){
int a, b , ans = 0;
cin>> a,b;
for (int j = a; j <= b; ++j)
{
if(isPrime(j)){
ans ++;
}
}
double d = ans/(r-l+1);
cout<<d;
}
}
Constraints:
1 ≤ Cases ≤ 100000
1 ≤ A≤ B ≤ 1000000
How can I optimize it further?
What I researched -
I should check if a i divides n only up till Math.sqrt(n)+1. Also I should do i = i+2 as I have checked for even numbers before only. I should also break the loop once ans becomes false so as to stop any further unnecessary iterations.
for(int i = 3; i<(Math.sqrt(n)+1);i=i+2){
if(n%i == 0){
ans = false;
break;
}
}
Here is the link to the question: codechef.
\$\endgroup\$
• \$\begingroup\$ "How can I optimize it further?" Lookup The sieve of Erasthotenes. \$\endgroup\$ – πάντα ῥεῖ Feb 18 '18 at 12:29
• \$\begingroup\$ Guys please do not down vote the question just because you don't know it. At least notify me in the comments what the question is lacking \$\endgroup\$ – Arhaan Ahmad Feb 18 '18 at 12:29
• 4
\$\begingroup\$ "... what the question is lacking" Research and efforts. \$\endgroup\$ – πάντα ῥεῖ Feb 18 '18 at 12:30
• \$\begingroup\$ I have a vague recollection of a formula to estimate the number of prime numbers less than a certain number, which relies on the Riemann hypothesis. Are you sure you need to count them one by one? \$\endgroup\$ – papagaga Feb 18 '18 at 13:22
• 2
\$\begingroup\$ "please do not down vote the question just because you don't know it" That's a dangerous assumption. Questions get downvoted if they lack quality. If anything, difficult questions tend to attract a lot of upvotes if they're well stated. \$\endgroup\$ – Mast Feb 18 '18 at 14:38
8
\$\begingroup\$
Your question contains 2 pieces of code which makes it hard to review.
Issue specific to the C++ code
Your are using ++i in your code despite having handled the even numbers explicitely before. It should be i+=2 like in your Java code.
Issue in both implementations
Instead of maintaining an ans boolean value, you can simply return false whenever you know that the number can't be prime.
You write your loop like this for(int i = 3; i<(Math.sqrt(n)+1);i=i+2) which is likely to compute the square root at each iteration. The compiler may be able to optimize this out but just in case, it is probably better to store it in a variable beforehand.
Different algorithm
To know whether many numbers are primes, a convenient and efficient algorithm is to use The Sieve of Eratosthenes to build a table to check primes.
You could build it one and for all to get the primes up to the maximum r value.
Going further, you could also build (once) a table giving for each number n the number of primes numbers smaller or equal to n. Then, for each input (a, b), the frequency is something along the lines of ( primes_up_to(b) - primes_up_to(a) / (b - a).
\$\endgroup\$
Your Answer
By clicking “Post Your Answer”, you agree to our terms of service, privacy policy and cookie policy
Not the answer you're looking for? Browse other questions tagged or ask your own question.
|
{
"url": "https://codereview.stackexchange.com/questions/187800/find-the-probability-of-picking-a-prime-number-in-a-range",
"source_domain": "codereview.stackexchange.com",
"snapshot_id": "crawl=CC-MAIN-2019-35",
"warc_metadata": {
"Content-Length": "145296",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:IPZPFFFZPGIQ6GNPADURINXCQ4N6XNEZ",
"WARC-Concurrent-To": "<urn:uuid:129b8bed-0219-42bd-8b2a-8a7609c7e8af>",
"WARC-Date": "2019-08-19T02:56:25Z",
"WARC-IP-Address": "151.101.1.69",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:ZPM4S4GK7Y4JYU2T36IVXDX52ETLHUHH",
"WARC-Record-ID": "<urn:uuid:7a50381b-fe9a-4373-a3b9-c38824fe93ac>",
"WARC-Target-URI": "https://codereview.stackexchange.com/questions/187800/find-the-probability-of-picking-a-prime-number-in-a-range",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:b55cde45-628c-4292-93c2-0677af6a9824>"
},
"warc_info": "isPartOf: CC-MAIN-2019-35\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for August 2019\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-159.ec2.internal\r\nsoftware: Apache Nutch 1.15 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.1-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
2,
18,
19,
32,
33,
209,
210,
230,
244,
288,
333,
367,
405,
439,
473,
474,
504,
542,
574,
601,
619,
633,
708,
709,
719,
720,
726,
768,
796,
816,
841,
851,
877,
902,
912,
939,
964,
974,
988,
1038,
1064,
1093,
1116,
1130,
1141,
1161,
1167,
1169,
1170,
1396,
1397,
1506,
1507,
1527,
1545,
1566,
1587,
1607,
1623,
1644,
1650,
1677,
1698,
1704,
1749,
1755,
1777,
1802,
1821,
1831,
1837,
1853,
1855,
1867,
1882,
1899,
1931,
1959,
1978,
2015,
2025,
2053,
2077,
2091,
2101,
2133,
2150,
2156,
2157,
2159,
2160,
2173,
2174,
2193,
2194,
2213,
2214,
2245,
2246,
2266,
2267,
2503,
2504,
2546,
2568,
2593,
2612,
2622,
2628,
2629,
2673,
2674,
2688,
2821,
3028,
3034,
3157,
3419,
3425,
3723,
3725,
3741,
3742,
3813,
3814,
3845,
3846,
3980,
3981,
4011,
4012,
4135,
4136,
4393,
4394,
4414,
4415,
4563,
4564,
4644,
4645,
4895,
4896,
4910,
4911,
4923,
4924,
5024,
5025
],
"line_end_idx": [
2,
18,
19,
32,
33,
209,
210,
230,
244,
288,
333,
367,
405,
439,
473,
474,
504,
542,
574,
601,
619,
633,
708,
709,
719,
720,
726,
768,
796,
816,
841,
851,
877,
902,
912,
939,
964,
974,
988,
1038,
1064,
1093,
1116,
1130,
1141,
1161,
1167,
1169,
1170,
1396,
1397,
1506,
1507,
1527,
1545,
1566,
1587,
1607,
1623,
1644,
1650,
1677,
1698,
1704,
1749,
1755,
1777,
1802,
1821,
1831,
1837,
1853,
1855,
1867,
1882,
1899,
1931,
1959,
1978,
2015,
2025,
2053,
2077,
2091,
2101,
2133,
2150,
2156,
2157,
2159,
2160,
2173,
2174,
2193,
2194,
2213,
2214,
2245,
2246,
2266,
2267,
2503,
2504,
2546,
2568,
2593,
2612,
2622,
2628,
2629,
2673,
2674,
2688,
2821,
3028,
3034,
3157,
3419,
3425,
3723,
3725,
3741,
3742,
3813,
3814,
3845,
3846,
3980,
3981,
4011,
4012,
4135,
4136,
4393,
4394,
4414,
4415,
4563,
4564,
4644,
4645,
4895,
4896,
4910,
4911,
4923,
4924,
5024,
5025,
5115
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 5115,
"ccnet_original_nlines": 149,
"rps_doc_curly_bracket": 0.008993159979581833,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3232830762863159,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.015075379982590675,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.3693467378616333,
"rps_doc_frac_unique_words": 0.4334239065647125,
"rps_doc_mean_word_length": 4.311141490936279,
"rps_doc_num_sentences": 49,
"rps_doc_symbol_to_word_ratio": 0.0025125599931925535,
"rps_doc_unigram_entropy": 5.275655746459961,
"rps_doc_word_count": 736,
"rps_doc_frac_chars_dupe_10grams": 0.03403719142079353,
"rps_doc_frac_chars_dupe_5grams": 0.13709422945976257,
"rps_doc_frac_chars_dupe_6grams": 0.12196659296751022,
"rps_doc_frac_chars_dupe_7grams": 0.08887487649917603,
"rps_doc_frac_chars_dupe_8grams": 0.07752914726734161,
"rps_doc_frac_chars_dupe_9grams": 0.05924991890788078,
"rps_doc_frac_chars_top_2gram": 0.020170189440250397,
"rps_doc_frac_chars_top_3gram": 0.014182159677147865,
"rps_doc_frac_chars_top_4gram": 0.014182159677147865,
"rps_doc_books_importance": -458.41357421875,
"rps_doc_books_importance_length_correction": -458.41357421875,
"rps_doc_openwebtext_importance": -287.4175720214844,
"rps_doc_openwebtext_importance_length_correction": -287.4175720214844,
"rps_doc_wikipedia_importance": -146.56015014648438,
"rps_doc_wikipedia_importance_length_correction": -146.56015014648438
},
"fasttext": {
"dclm": 0.9613336324691772,
"english": 0.7843528985977173,
"fineweb_edu_approx": 2.609194278717041,
"eai_general_math": 0.9633153080940247,
"eai_open_web_math": 0.26759445667266846,
"eai_web_code": 0.3567315340042114
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "512.7",
"labels": {
"level_1": "Science and Natural history",
"level_2": "Mathematics",
"level_3": "Algebra"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "4",
"label": "Analyze"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "4",
"label": "Code/Software"
},
"secondary": {
"code": "5",
"label": "Social/Forum"
}
},
"extraction_artifacts": {
"primary": {
"code": "1",
"label": "Leftover HTML"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "2",
"label": "Partially Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-1,418,503,565,179,736,600
|
1
I have a SharePoint list containing 2 lookup columns (department and manager). How do I update values to SP list upon edit in gridview?
The following is the code for an update method :
public void updateRow(string itemID, string firstName, string lastName, string age, string eAddress, string department, string manager, string gender, string salary)
{
ClientContext clientContext = new ClientContext("https://xyz.xyz.com/sites/xyz/TrainingSite/");
try
{
SP.List oList = clientContext.Web.Lists.GetByTitle("Employees");
SP.CamlQuery camlQuery = new SP.CamlQuery();
camlQuery.ViewXml = @"<Query><Where><Eq><FieldRef Name='ID' /><Value Type='Counter'>" + itemID + "</Value></Eq></Where></Query>";
SP.ListItemCollection itemInfo = oList.GetItems(camlQuery);
clientContext.Load(itemInfo);
clientContext.ExecuteQuery();
foreach (SP.ListItem item in itemInfo)
{
if (itemID == item["ID"].ToString())
{
item["Title"] = firstName;
item["Last_x0020_Name"] = lastName;
item["u5ib"] = age;
item["Address"] = eAddress;
//Department column
//item["Department"] = department;
FieldLookupValue deptItem = new FieldLookupValue();
//deptItem.LookupId = Convert.ToInt32(TextBoxEditDepartment.SelectedValue); // here instead of 1, you should provide corresponding Department list item ID
item["Department"] = deptItem;
deptItem.LookupId = Convert.ToInt32(department);
item.Update();
//Manager column
//item["Manager"] = manager;
FieldLookupValue mgrItem = new FieldLookupValue();
item["Manager"] = mgrItem;
mgrItem.LookupId = Convert.ToInt32(manager);
item.Update();
item["Gender"] = gender;
item["Salary"] = salary;
item.Update();
break;
}
}
clientContext.ExecuteQuery();
}
Following is the code for RowUpdating event:
protected void gridview_RowUpdating(object sender, GridViewUpdateEventArgs e)
{
//Omitted few lines for clarity
DropDownList department = (DropDownList)gridview.Rows[e.RowIndex].Cells[4].FindControl("ddlDepartment"); //department
DropDownList manager = (DropDownList)gridview.Rows[e.RowIndex].Cells[5].FindControl("ddlManager"); //manager
//Omitted few lines for clarity
updateRow(itemID.Text, firstName.Text, lastName.Text, age.Text, eAddress.Text, department.Text, manager.Text, gender.Text, salary.Text); // call update method
gridview.EditIndex = -1; //Turn the Grid to read only mode
BindGrid(); // Rebind GridView to reflect changes made
Response.Write("Update Seccessful!");
}
I get an error like :"Input string was not in the correct format" for the following lines :
FieldLookupValue deptItem = new FieldLookupValue();
item["Department"] = deptItem;
deptItem.LookupId = Convert.ToInt32(department);
item.Update();
Please provide a solution :) Thanks!
1 Answer 1
1
You should interchange the lines in your code.
FieldLookupValue deptItem = new FieldLookupValue();
deptItem.LookupId = Convert.ToInt32(department); //department should be department list item ID because its a lookup ID
item["Department"] = deptItem;
item.Update();
Hope this helps to you :)
5
• I still get that Input string was not in correct format error, when i debug it reads the value of the first lookup and throws this error @Nagababu
– Sanjana V
Commented Aug 14, 2017 at 11:32
• what is department.Text value in your code. I mean it's like 'HR Department' or '1' (look up ID) Commented Aug 14, 2017 at 11:35
• Its like 'HR Department' @Nagababu
– Sanjana V
Commented Aug 14, 2017 at 11:43
• 1
Ok, here you should provide the ID for LookupID like '1'. Verify the other properties of Department like ID or Value instead of Text. Commented Aug 14, 2017 at 11:46
• that works well with department.ID, But how does update happen? I cannot hard code the id of the textboxes in edit mode and pass those id's to the objects.. That doesn't seem to be a good method! How else does update take place? @Nagababu
– Sanjana V
Commented Aug 16, 2017 at 7:32
Your Answer
By clicking “Post Your Answer”, you agree to our terms of service and acknowledge you have read our privacy policy.
Not the answer you're looking for? Browse other questions tagged or ask your own question.
|
{
"url": "https://sharepoint.stackexchange.com/questions/223247/update-for-sharepoint-list-containing-lookup-columns",
"source_domain": "sharepoint.stackexchange.com",
"snapshot_id": "CC-MAIN-2024-38",
"warc_metadata": {
"Content-Length": "165989",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:AJ223DUAQUYJWIJWRAB2AOONH5VVA3U2",
"WARC-Concurrent-To": "<urn:uuid:362039c5-c5c4-479a-897f-6f4dd259a34c>",
"WARC-Date": "2024-09-15T02:56:19Z",
"WARC-IP-Address": "172.64.144.30",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:5S5DDFD34QOBA7YI4GVUQLUSPBQSM3VV",
"WARC-Record-ID": "<urn:uuid:6b0630d5-302c-4880-9be8-aa6c5c2bed28>",
"WARC-Target-URI": "https://sharepoint.stackexchange.com/questions/223247/update-for-sharepoint-list-containing-lookup-columns",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:967f5418-0f18-44df-920f-ba7e1b360736>"
},
"warc_info": "isPartOf: CC-MAIN-2024-38\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for September 2024\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-65\r\nsoftware: Apache Nutch 1.20 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.5-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
2,
3,
139,
140,
189,
190,
356,
362,
466,
467,
479,
489,
566,
623,
765,
837,
879,
921,
972,
986,
1039,
1057,
1104,
1160,
1200,
1248,
1249,
1289,
1344,
1416,
1591,
1642,
1711,
1746,
1747,
1784,
1833,
1904,
1951,
2016,
2051,
2052,
2097,
2142,
2177,
2204,
2222,
2236,
2278,
2288,
2289,
2334,
2335,
2413,
2419,
2420,
2452,
2453,
2579,
2696,
2697,
2741,
2742,
2909,
2910,
2977,
3040,
3041,
3087,
3093,
3094,
3186,
3187,
3259,
3310,
3379,
3414,
3415,
3452,
3453,
3464,
3465,
3467,
3468,
3515,
3516,
3568,
3689,
3720,
3735,
3736,
3762,
3763,
3765,
3916,
3932,
3968,
4101,
4140,
4156,
4192,
4198,
4368,
4611,
4627,
4662,
4663,
4675,
4676,
4792,
4793
],
"line_end_idx": [
2,
3,
139,
140,
189,
190,
356,
362,
466,
467,
479,
489,
566,
623,
765,
837,
879,
921,
972,
986,
1039,
1057,
1104,
1160,
1200,
1248,
1249,
1289,
1344,
1416,
1591,
1642,
1711,
1746,
1747,
1784,
1833,
1904,
1951,
2016,
2051,
2052,
2097,
2142,
2177,
2204,
2222,
2236,
2278,
2288,
2289,
2334,
2335,
2413,
2419,
2420,
2452,
2453,
2579,
2696,
2697,
2741,
2742,
2909,
2910,
2977,
3040,
3041,
3087,
3093,
3094,
3186,
3187,
3259,
3310,
3379,
3414,
3415,
3452,
3453,
3464,
3465,
3467,
3468,
3515,
3516,
3568,
3689,
3720,
3735,
3736,
3762,
3763,
3765,
3916,
3932,
3968,
4101,
4140,
4156,
4192,
4198,
4368,
4611,
4627,
4662,
4663,
4675,
4676,
4792,
4793,
4883
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 4883,
"ccnet_original_nlines": 111,
"rps_doc_curly_bracket": 0.0018431299831718206,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.17754867672920227,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.029782360419631004,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.3814432919025421,
"rps_doc_frac_unique_words": 0.47780126333236694,
"rps_doc_mean_word_length": 6.560253620147705,
"rps_doc_num_sentences": 68,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 5.107479572296143,
"rps_doc_word_count": 473,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.17241379618644714,
"rps_doc_frac_chars_dupe_6grams": 0.0331936813890934,
"rps_doc_frac_chars_dupe_7grams": 0.02384788915514946,
"rps_doc_frac_chars_dupe_8grams": 0.02384788915514946,
"rps_doc_frac_chars_dupe_9grams": 0.02384788915514946,
"rps_doc_frac_chars_top_2gram": 0.01933613047003746,
"rps_doc_frac_chars_top_3gram": 0.018047049641609192,
"rps_doc_frac_chars_top_4gram": 0.023203350603580475,
"rps_doc_books_importance": -400.17633056640625,
"rps_doc_books_importance_length_correction": -400.17633056640625,
"rps_doc_openwebtext_importance": -222.8532257080078,
"rps_doc_openwebtext_importance_length_correction": -222.8532257080078,
"rps_doc_wikipedia_importance": -98.73448181152344,
"rps_doc_wikipedia_importance_length_correction": -98.73448181152344
},
"fasttext": {
"dclm": 0.6248176097869873,
"english": 0.6129408478736877,
"fineweb_edu_approx": 2.514360189437866,
"eai_general_math": 0.042243119329214096,
"eai_open_web_math": 0.09045630693435669,
"eai_web_code": 0.0039452300406992435
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.74",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "2",
"label": "Partially Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "4",
"label": "Graduate/Expert Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-4,026,028,191,570,349,600
|
Techniques for WCAG 2.0
Skip to Content (Press Enter)
This document is a draft, and is designed to show changes from a previous version. It is presently showing added text,changed text,deleted text,[start]/[end] markers,and Issue Numbers.
Hide All Edits | Toggle Deletions | Toggle Issue Numbers | Toggle [start]/[end] Markers | Show All Edits
Changes are displayed as follows:
-
G139: Creating a mechanism that allows users to jump to errors
Applicability
Content that accepts user data input, with restrictions on the format, value, and/or type of the input.
This technique relates to:
Description
The objective of this technique is to help users find input errors where the information supplied by the user is not accepted. This includes fields with missing required information and fields with incorrect information. When users enter data input that is checked, and input errors are detected, a link to that error is provided so that the user does not have to search for it. One approach is to use server-side validation, and to re-display the form (including any previously entered data), and a text description at the top of the page that indicates the fact that there was an input error, describes the nature of the problem, and provides a link the field(s) with a problem.
Examples
Example 1: Server-side error checking
The user inputs invalid data on a form field and submits the form. The server returns the form, with the user's data still present, and indicates clearly in text at the top of the page that there were not accepted. The text describes the nature of the error(s) and provides a link to the field that had the problem so the user can easily navigate to it to fix the problem.
Example 2: Client-side error checking with a popup
The user inputs invalid data on a form field and attempts to submit the form. Client-side scripting detects the error, cancels the submit, and modifies the document to provide a text message describing the error, with links to the field(s) with the error. The script also modifies the labels of the fields with the problems to highlight them.
Example 3: Client-side error checking with no popup
When the user submits a form, instead of taking them to a new page, a script automatically sets focus to a text link that says "Errors have occurred." The link goes to the first item in an ordered list of descriptive error messages.[begin delete]"[end delete] Each list item is a link to the control where the error had occurred. And there is a link from the error back to the ordered list of descriptive error messages. The process is repeated as needed.
Tests
Procedure
1. Fill out a form, deliberately leaving a required (mandatory) field blank, and make an input error on another field and submit the form.
2. Check that a text message is provided that identifies the field that is missing required data.
3. Check that a text message is provided that identifies the field with the input error.
4. Check that there is a link to each field that [begin delete]has [end delete]is missing required data from the missing data message
5. Check that there is a link to the list of errors from the error message.
Note: Success Criterion 3.3.2 requires that if an input error is detected and suggestions for correction are known and can be provided without jeopardizing the security or purpose of the content, the suggestions are provided to the user.
Expected Results
|
{
"url": "http://www.w3.org/WAI/GL/2010/WD-WCAG20-TECHS-20100617/G139",
"source_domain": "www.w3.org",
"snapshot_id": "crawl=CC-MAIN-2017-04",
"warc_metadata": {
"Content-Length": "11646",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:PUC332BKH5CPMAECGBZMINU23AF7CU62",
"WARC-Concurrent-To": "<urn:uuid:d142222e-dd70-40a6-955d-7ddd0c9a5d5a>",
"WARC-Date": "2017-01-24T09:47:54Z",
"WARC-IP-Address": "128.30.52.100",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:DN37ENUPFKIXNSCX2BRRPNOMZN4MWQHY",
"WARC-Record-ID": "<urn:uuid:be8eeb18-73bf-4035-9566-72fa8881539a>",
"WARC-Target-URI": "http://www.w3.org/WAI/GL/2010/WD-WCAG20-TECHS-20100617/G139",
"WARC-Truncated": "length",
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:d339881c-9615-4b8f-98f5-d966fcc5cdcd>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-171-10-70.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2017-04\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web for January 2017\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
24,
25,
55,
56,
241,
242,
362,
363,
397,
398,
400,
401,
464,
465,
479,
480,
584,
585,
612,
613,
625,
626,
1307,
1308,
1317,
1318,
1356,
1357,
1730,
1731,
1782,
1783,
2126,
2127,
2179,
2180,
2636,
2637,
2643,
2644,
2654,
2655,
2796,
2797,
2897,
2898,
2989,
2990,
3126,
3127,
3205,
3206,
3444,
3445
],
"line_end_idx": [
24,
25,
55,
56,
241,
242,
362,
363,
397,
398,
400,
401,
464,
465,
479,
480,
584,
585,
612,
613,
625,
626,
1307,
1308,
1317,
1318,
1356,
1357,
1730,
1731,
1782,
1783,
2126,
2127,
2179,
2180,
2636,
2637,
2643,
2644,
2654,
2655,
2796,
2797,
2897,
2898,
2989,
2990,
3126,
3127,
3205,
3206,
3444,
3445,
3461
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 3461,
"ccnet_original_nlines": 54,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3767908215522766,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.002865330083295703,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.15902578830718994,
"rps_doc_frac_unique_words": 0.3732638955116272,
"rps_doc_mean_word_length": 4.723958492279053,
"rps_doc_num_sentences": 32,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.6747565269470215,
"rps_doc_word_count": 576,
"rps_doc_frac_chars_dupe_10grams": 0.06762219965457916,
"rps_doc_frac_chars_dupe_5grams": 0.14369717240333557,
"rps_doc_frac_chars_dupe_6grams": 0.0999632477760315,
"rps_doc_frac_chars_dupe_7grams": 0.0999632477760315,
"rps_doc_frac_chars_dupe_8grams": 0.06762219965457916,
"rps_doc_frac_chars_dupe_9grams": 0.06762219965457916,
"rps_doc_frac_chars_top_2gram": 0.012862919829785824,
"rps_doc_frac_chars_top_3gram": 0.012862919829785824,
"rps_doc_frac_chars_top_4gram": 0.011025359854102135,
"rps_doc_books_importance": -275.32952880859375,
"rps_doc_books_importance_length_correction": -275.32952880859375,
"rps_doc_openwebtext_importance": -161.57896423339844,
"rps_doc_openwebtext_importance_length_correction": -161.57896423339844,
"rps_doc_wikipedia_importance": -114.41580200195312,
"rps_doc_wikipedia_importance_length_correction": -114.41580200195312
},
"fasttext": {
"dclm": 0.5446324944496155,
"english": 0.8760521411895752,
"fineweb_edu_approx": 2.308260202407837,
"eai_general_math": 0.8510693311691284,
"eai_open_web_math": 0.4358482360839844,
"eai_web_code": 0.6987472772598267
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.678",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "10",
"label": "Knowledge Article"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
7,236,705,116,086,919,000
|
ChangeLog 373 KB
Newer Older
Niels Möller's avatar
Niels Möller committed
1 2
2018-07-12 Niels Möller <nisse@lysator.liu.se>
3 4 5
* examples/eratosthenes.c (main): Don't allocate bitmap storage
for limit == 2 (early exit), closing memory leak at exit.
Niels Möller's avatar
Niels Möller committed
6 7
* eccdata.c (output_curve): Replace mpz_init_set_ui by mpz_set_ui,
to fix memory leak.
8 9
(ecc_curve_clear): New function.
(main): Call it, to deallocate storage before exit.
Niels Möller's avatar
Niels Möller committed
10
11 12 13 14 15 16
2018-07-08 Niels Möller <nisse@lysator.liu.se>
* fat-x86_64.c (fat_init): Fix setup for nettle_sha1_compress.
* x86_64/fat/sha1-compress.asm: Add leading underscore to symbol name.
* x86_64/fat/sha1-compress-2.asm: Likewise.
Niels Möller's avatar
Niels Möller committed
17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40
2018-07-07 Niels Möller <nisse@lysator.liu.se>
From Nikos Mavrogiannopoulos.
* sha1-compress.c (nettle_sha1_compress): Renamed, and promoted to
public function, since there's known appliation usage (filezilla).
* sha1.h (_nettle_sha1_compress): Old name, now a preprocessor
alias for the new name.
* md5-compress.c (nettle_md5_compress): Similarly renamed (used by
sogo).
* md5.h (_nettle_md5_compress): Old name,, now a preprocessor
alias for the new name.
* chacha-internal.h, dsa-internal.h, eddsa-internal.h:
* hogweed-internal.h, ripemd160-internal.h, rsa-internal.h:
* salsa20-internal.h, sha2-internal.h, sha3-internal.h:
* umac-internal.h: Internal declarations moved to new header
files, which are not installed..
* Makefile.in (DISTFILES): Added above files.
* libnettle.map.in: Use a different symbol version for _nettle_*
symbols, depending on the minor release. This marks these symbols
explicitly not part of the public Nettle ABI.
* libhogweed.map.in: Analogous change.
41 42
2018-06-17 Niels Möller <nisse@lysator.liu.se>
43 44 45
* aclocal.m4 (NETTLE_CHECK_IFUNC): Fix quoting. Patch contributed
by Dmitry Eremin-Solenikov.
46 47 48 49
* testsuite/symbols-test: Exclude ____chkstk_darwin symbols,
produced by Apple's Xcode 10 compiler. Patch contributed by
Dominyk Tiller.
50 51 52 53 54 55 56 57 58 59 60 61 62 63 64
2018-03-25 Niels Möller <nisse@lysator.liu.se>
From Michael Weiser.
* configure.ac (ASM_WORDS_BIGENDIAN): New substution, set from AC_C_BIGENDIAN.
* config.m4.in: Use it to set WORDS_BIGENDIAN.
* asm.m4 (IF_BE, IF_LE): New macros.
* arm/memxor.asm: Support big-endian ARM.
* arm/memxor3.asm: Likewise.
* arm/neon/chacha-core-internal.asm: Likewise.
* arm/neon/salsa20-core-internal.asm: Likewise.
* arm/neon/umac-nh.asm: Likewise.
* arm/v6/sha1-compress.asm: Likewise.
* arm/v6/sha256-compress.asm: Likewise.
* arm/README: Document big-endian considerations.
65 66 67 68 69 70 71 72 73 74 75 76 77 78 79
2018-03-17 Niels Möller <nisse@lysator.liu.se>
Discourage direct access to data symbols with non-public size.
Direct references to these symbols may result in copy-relocations
like R_X86_64_COPY, which make the symbol size leak into the ABI.
* ecc-curve.h (_nettle_secp_192r1, _nettle_secp_224r1)
(_nettle_secp_256r1, _nettle_secp_384r1, _nettle_secp_521r1): Add
leading underscore on these data symbols.
* nettle-meta.h (_nettle_ciphers, _nettle_hashes, _nettle_aeads)
(_nettle_armors): Add leading underscore on these data symbols.
Update all internal use. Macros without leading underscore remain,
and expand to access via accessor functions nettle_get_ciphers and
similar.
Niels Möller's avatar
Niels Möller committed
80 81
2018-03-10 Niels Möller <nisse@lysator.liu.se>
82 83 84
* eccdata.c (ecc_table_size): New helper function.
(ecc_pippenger_precompute): Display warning for poor parameters.
Niels Möller's avatar
Niels Möller committed
85 86 87
* eccparams.c (main): New program, to list parameter alternatives
for Pippenger's algorithm.
88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104
* Makefile.in: Tweak parameters for ecc tables.
(ecc-192.h): Change parameters from k = 7, c = 6 to k = 8, c = 6.
Reduces table size from 15 KB to 12 KB. Modest speedup, appr. 3%
for ecdsa signatures.
(ecc-224.h): Change parameters from k = 12, c = 6 to k = 16, c =
7. Table size unchanged (14 KB in 32-bit platforms, 18 KB on
64-bit platforms. Minor speedup, appr. 1% for ecdsa signatures.
(ecc-256.h): Change parameters from k = 14, c = 6 to k = 11, c =
6. Table size unchanged, 16 KB. 14% speedup for ecdsa signatures.
(ecc-384.h): Changed parameters from k = 41, c = 6 to k = 32, c =
6. Table size unchanged. 12% speedup for ecdsa signatures.
(ecc-521.h): Changed parameters from k = 56, c = 6 to k 44, c = 6.
Table size unchanged (17 KB on 32-bit platforms, 18 KB on 64-bit
platforms). 15% speedup for ecdsa signatures.
(ecc-255.h): Change parameters from k = 14, c = 6 to k = 11, c =
6. Table size unchanged, 16 KB. 24% speedup for eddsa signatures.
105 106 107 108 109
2018-03-14 Niels Möller <nisse@lysator.liu.se>
Merge sha256 code using the x86_64 sha_ni instructions, starting
2018-02-21.
110 111 112 113 114 115 116
2018-03-11 Niels Möller <nisse@lysator.liu.se>
* x86_64/fat/sha256-compress.asm: New file.
* x86_64/fat/sha256-compress-2.asm: New file.
* fat-x86_64.c (fat_init): Select plain x86_64 assembly version or
sha_ni version for sha256_compress.
117 118 119 120 121
2018-02-21 Niels Möller <nisse@lysator.liu.se>
* x86_64/sha_ni/sha256-compress.asm: New implementation using sha_ni
instructions.
122 123 124 125
2018-02-20 Niels Möller <nisse@lysator.liu.se>
* testsuite/cmac-test.c (test_cmac_hash): Deallocate ctx properly.
126 127 128 129 130 131 132 133 134 135 136 137 138
2018-02-19 Niels Möller <nisse@lysator.liu.se>
Mostly aesthetic changes. Besides indentation:
* cmac.h (struct cmac128): Rename, to cmac128_ctx.
(CMAC128_CTX): Rename first member from data to ctx.
* cmac.c: Use const void * as the type for cipher arguments.
(block_mulx): Un-inline.
(cmac128_set_key): Make a constant function local.
* testsuite/cmac-test.c: Delete local typedefs.
2018-02-19 Nikos Mavrogiannopoulos <nmav@redhat.com>
139 140 141 142 143 144 145 146 147 148 149 150 151 152 153 154 155 156 157 158 159
Add support for CMAC.
* cmac.h: New file.
(struct cmac128): New struct.
* cmac.c (block_mulx, cmac128_set_key, cmac128_update)
(cmac128_digest): New file, new functions.
* cmac-aes128.c (cmac_aes128_set_key, cmac_aes128_update)
(cmac_aes128_digest): New file, new functions.
* cmac-aes256.c (cmac_aes256_set_key, cmac_aes256_update)
(cmac_aes256_digest): New file, new functions.
* Makefile.in (nettle_SOURCES): Added cmac.c cmac-aes128.c cmac-aes256.c.
(HEADERS): Added cmac.h.
* testsuite/cmac-test.c: New tests.
* testsuite/Makefile.in (TS_NETTLE_SOURCES): Add cmac-test.c.
* examples/nettle-benchmark.c (time_cmac): New function.
(main): Use it.
* nettle.texinfo: Document CMAC.
160 161
2018-02-20 Niels Möller <nisse@lysator.liu.se>
162
* testsuite/cbc-test.c (test_cbc_bulk): Use struct
163
aes256_ctx, instead of the deprecated struct aes_ctx.
164 165
* testsuite/cfb-test.c (test_cfb_bulk): Likewise.
* examples/rsa-session.h (struct rsa_session): Likewise.
166 167 168 169 170
* examples/rsa-encrypt.c (rsa_session_set_encrypt_key)
(process_file): Use aes256_* functions.
* examples/rsa-decrypt.c (rsa_session_set_decrypt_key)
(process_file): Likewise.
171 172 173 174 175 176 177 178 179 180 181 182
2018-02-19 Niels Möller <nisse@lysator.liu.se>
* nettle-internal.h: Include sha3.h, needed for the definition of
NETTLE_MAX_HASH_CONTEXT_SIZE.
(TMP_DECL_ALIGN, TMP_ALLOC_ALIGN): New macros, to support
allocation of context structs with alignment requirements.
[!HAVE_ALLOCA]: Also use assert, rather than calling abort
directly.
* pss.c (pss_encode_mgf1, pss_verify_mgf1): Use new macros.
* pss-mgf1.c (pss_mgf1): Likewise.
183 184 185 186 187 188
2018-02-18 Niels Möller <nisse@lysator.liu.se>
* testsuite/Makefile.in (TS_NETTLE_SOURCES): Moved pss-mgf1-test.c...
(TS_HOGWEED_SOURCES): ...to here. Fixes link failure in builds
without public-key support.
Niels Möller's avatar
Niels Möller committed
189 190 191 192 193
2018-02-18 Dmitry Eremin-Solenikov <dbaryshkov@gmail.com>
* examples/nettle-openssl.c): Move expressions with side effects
out of asserts.
194 195 196 197 198 199 200 201 202 203 204
2018-02-17 Dmitry Eremin-Solenikov <dbaryshkov@gmail.com>
(openssl_evp_set_encrypt_key, openssl_evp_set_decrypt_key): Use
EVP_CipherInit_ex.
* examples/nettle-openssl.c (nettle_openssl_gcm_aes128)
(nettle_openssl_gcm_aes192, nettle_openssl_gcm_aes256): New aead
algorithms, for benchmarking purposes, and supporting wrapper functions.
* nettle-internal.h: Corresponding declarations.
* examples/nettle-benchmark.c (main): Include openssl's gcm aes in
benchmark.
205 206
2018-02-16 Niels Möller <nisse@lysator.liu.se>
207 208 209
* nettle.texinfo: Improved index entries.
(Cipher functions): Update CAST128/CAST5 docs. Inconsistencies
spotted by Henrik Rindlöw.
210
211 212 213 214
2018-02-10 Niels Möller <nisse@lysator.liu.se>
* configure.ac: New configure option --enable-x86-sha-ni.
215 216 217 218 219 220 221
2018-02-07 Niels Möller <nisse@lysator.liu.se>
* x86_64/fat/sha1-compress.asm: New file.
* x86_64/fat/sha1-compress-2.asm: New file.
* fat-x86_64.c (fat_init): Select plain x86_64 assembly version or
sha_ni version for sha1_compress.
222 223
2018-02-05 Niels Möller <nisse@lysator.liu.se>
224 225 226
* x86_64/sha_ni/sha1-compress.asm: New implementation using sha_ni
instructions.
227 228 229 230
* fat-x86_64.c (get_x86_features): Check for sha_ni extension.
* x86_64/fat/cpuid.asm: Clear %ecx input to cpuid instruction.
231 232 233 234 235 236
2018-02-01 Nikos Mavrogiannopoulos <nmav@redhat.com>
* gcm.c (gcm_fill): New function, for use with _ctr_crypt16.
(gcm_encrypt, gcm_decrypt): Use _ctr_crypt16. 50% speedup of
gcm_aes128, benchmarked on x86_64 with aesni instructions.
237 238 239 240 241 242 243 244 245 246 247 248 249 250 251 252 253 254
2018-02-01 Niels Möller <nisse@lysator.liu.se>
Based on a patch contributed by Nikos Mavrogiannopoulos.
* ctr16.c (_ctr_crypt16): New file, renamed and generalized
function. New function pointer argument, used to fill a block with
counter values. Use nettle_block16 * as the type for the buffer to
be filled. Always process any final and partial block, and return
no value.
* ctr.c (ctr_crypt): ... previous, replaced, function.
(ctr_fill16): Updated to new argument type.
(ctr_crypt): Return immediately after using _ctr_crypt16.
* ctr-internal.h: New file, declaring _ctr_crypt16.
(nettle_fill16_func): New function typedef.
* Makefile.in (nettle_SOURCES): Added ctr16.c.
(DISTFILES): Added ctr-internal.h.
255 256 257 258
2018-01-30 Niels Möller <nisse@lysator.liu.se>
* Makefile.in (clean-here): Don't delete desdata.stamp.
259 260 261 262 263 264 265 266 267
2018-01-24 Jay Foad <jay.foad@gmail.com>
* Makefile.in (TARGETS): Delete dependencies on aesdata, desdata,
twofishdata, shadata and gcmdata. They are not needed for a normal
build.
(clean-here): Explicitly delete of above files.
(desdata.stamp): New stamp target, to avoid building desdata twice
in a parallell build.
Niels Möller's avatar
Niels Möller committed
268 269 270 271 272
2018-01-23 Niels Möller <nisse@lysator.liu.se>
* configure.ac (asm_path): Recognize "x86", in addition to "i?86",
for 32-bit x86 processors. Reportedly needed for x86 android builds.
Niels Möller's avatar
Niels Möller committed
273 274 275 276 277 278 279 280 281
2018-01-20 Niels Möller <nisse@lysator.liu.se>
CFB8 support, contributed by Dmitry Eremin-Solenikov.
* cfb.c (cfb8_encrypt, cfb8_decrypt): New functions.
* cfb.h: Declare them.
(CFB8_ENCRYPT, CFB8_DECRYPT): New macros.
* testsuite/cfb-test.c: New tests for CFB8.
* nettle.texinfo (CFB and CFB8): Documentation.
282 283 284 285
2018-01-16 Niels Möller <nisse@lysator.liu.se>
* tools/pkcs1-conv.c (convert_file): Add missing break statements.
Niels Möller's avatar
Niels Möller committed
286 287 288 289 290 291 292 293 294
2018-01-09 Niels Möller <nisse@lysator.liu.se>
* testsuite/testutils.c (test_cipher_ctr): Test operations with
shorter sizes.
* testsuite/ctr-test.c: Additional unofficial test vectors, to
exercise carry propagation in the counter, and block size
different from 16.
295 296
2018-01-08 Niels Möller <nisse@lysator.liu.se>
297 298 299 300 301 302 303
* ctr.c (ctr_crypt16): New function, with optimizations specific
to 16-byte block size.
(ctr_fill16): New helper function, definition depending on
WORDS_BIGENDIAN, and little endian version requiring
HAVE_BUILTIN_BSWAP64.
(ctr_crypt): Use ctr_crypt16, when appropriate.
304 305
* nettle-types.h (union nettle_block16): Add uint64_t field.
306 307 308
* configure.ac: Check for __builtin_bswap64, define
HAVE_BUILTIN_BSWAP64 if available.
Niels Möller's avatar
Niels Möller committed
309 310
* ctr.c (ctr_fill): New function. Use in ctr_crypt.
311 312 313 314
* ctr.c (ctr_crypt): For in-place operation, increase max buffer
size from 4 blocks to 512 bytes, similarly to CBC and CFB.
Improves in-place aes128 CTR performance by 25% on x86_64.
315 316 317
* examples/nettle-benchmark.c (time_cipher): Benchmark in-place
operation separately, for cbc_decrypt and ctr_crypt.
318 319 320 321 322
* cbc.c (cbc_decrypt): For in-place operation (src == dst case),
eliminate use of src variable.
* cfb.c (cfb_decrypt): Likewise.
* gcm.c (gcm_crypt): Likewise, and replace one memxor3 by memxor.
Niels Möller's avatar
Niels Möller committed
323 324 325 326 327 328 329
2018-01-03 Niels Möller <nisse@lysator.liu.se>
* x86_64/aesni/aes-encrypt-internal.asm: Read subkeys into xmm
registers before the block loop, and completely unroll the round
loop.
* x86_64/aesni/aes-decrypt-internal.asm: Likewise.
Niels Möller's avatar
Niels Möller committed
330 331
2017-11-19 Niels Möller <nisse@lysator.liu.se>
332
* Released nettle-3.4.
Niels Möller's avatar
Niels Möller committed
333
334 335 336 337 338 339
2017-11-12 Niels Möller <nisse@lysator.liu.se>
* configure.ac: Update check of GMP_NUMB_BITS declaration in
assembly files. Was broken by rename of configure variable
GMP_NUMB_BITS --> NUMB_BITS.
Niels Möller's avatar
Niels Möller committed
340 341 342 343 344 345 346 347
2017-11-11 Niels Möller <nisse@lysator.liu.se>
* nettle.texinfo: Document nettle_get_hashes, nettle_get_ciphers
and nettle_get_aeads, and replace nettle_secp_256r1 by
nettle_get_secp_256r1. Update version numbers. Delete ancient
setting of ispell-skip-region-alist as an emacs file-local
variable.
348 349 350 351 352 353 354 355 356 357
2017-11-08 Niels Möller <nisse@lysator.liu.se>
* ecc-curve.h (nettle_secp_192r1, nettle_secp_224r1)
(nettle_secp_256r1, nettle_secp_384r1, nettle_secp_521r1): Delete
macro wrappers, partially reverting below 2017-04-09 change. They
didn't work at all for applications that only see a forward
declaration of struct ecc_curve. Instead, we will have to make an
ABI and API break and delete these symbols, when the size of
struct ecc_curve is increased.
Niels Möller's avatar
Niels Möller committed
358 359 360 361 362 363
2017-11-05 Niels Möller <nisse@lysator.liu.se>
* configure.ac Bump package version to 3.4.
(LIBNETTLE_MINOR): Bump library version to 6.4.
(LIBHOGWEED_MINOR): Bump library version to 4.4.
Niels Möller's avatar
Niels Möller committed
364 365 366 367 368 369
2017-10-23 Niels Möller <nisse@lysator.liu.se>
* examples/Makefile.in (check): Also set DYLD_LIBRARY_PATH in the
environment, to support Mac OSX shared libraries.
* testsuite/Makefile.in (LD_LIBRARY_PATH): Likewise.
370 371
2017-10-23 Niels Möller <nisse@lysator.liu.se>
Niels Möller's avatar
Niels Möller committed
372
Merge API fixes, starting at 2017-01-12.
373
374 375
2017-04-09 Niels Möller <nisse@lysator.liu.se>
376 377 378 379 380 381 382 383
* ecc-curve.h (nettle_get_secp_192r1, nettle_get_secp_224r1)
(nettle_get_secp_256r1, nettle_get_secp_384r1)
(nettle_get_secp_521r1): New functions, returning a pointer to
corresponding structure.
(nettle_secp_192r1, nettle_secp_224r1, nettle_secp_256r1)
(nettle_secp_384r1, nettle_secp_521r1): Redefined as macros,
calling the corresponding function.
384 385
* nettle-meta.h (nettle_ciphers, nettle_aeads, nettle_armors): New
macros, analogous to below change to nettle_hashes.
386
Niels Möller's avatar
Niels Möller committed
387
* nettle-meta-ciphers.c (nettle_get_ciphers): New function.
388
Niels Möller's avatar
Niels Möller committed
389
* nettle-meta-aeads.c (nettle_get_aeads): New function.
Niels Möller's avatar
Niels Möller committed
390
Niels Möller's avatar
Niels Möller committed
391
* nettle-meta-armors.c (nettle_get_armors): New function.
392
393 394
2017-01-12 Niels Möller <nisse@lysator.liu.se>
Niels Möller's avatar
Niels Möller committed
395 396 397 398 399
* tools/nettle-hash.c (find_algorithm): Deleted function.
(main): Replaced by call to nettle_lookup_hash.
* testsuite/meta-hash-test.c (test_main): Use nettle_lookup_hash.
400 401 402 403 404 405
* nettle-meta.h (nettle_hashes): New macro, expanding to a call to
nettle_get_hashes. Direct access to the array causes the array
size to leak into the ABI, since a plain un-relocatable executable
linking with libnettle.so gets copy relocations for any referenced
data items in the shared library.
Niels Möller's avatar
Niels Möller committed
406
* nettle-meta-hashes.c (nettle_get_hashes): New function.
407
Niels Möller's avatar
Niels Möller committed
408 409 410 411 412 413 414 415 416 417 418 419
2017-10-16 Niels Möller <nisse@lysator.liu.se>
CFB support, contributed by Dmitry Eremin-Solenikov.
* cfb.c (cfb_encrypt, cfb_decrypt): New file, new functions.
* cfb.h: New header file.
(CFB_CTX, CFB_SET_IV, CFB_ENCRYPT, CFB_DECRYPT): New macros.
* Makefile.in (nettle_SOURCES): Add cfb.c.
(HEADERS): Add cfb.h.
* testsuite/cfb-test.c: New test case.
* testsuite/testutils.c (test_cipher_cfb): New function.
* nettle.texinfo (CFB): Documentation.
420 421 422 423 424
2017-10-16 Niels Möller <nisse@lysator.liu.se>
* aclocal.m4 (GMP_PROG_CC_FOR_BUILD): Add -g when compiling with
gcc.
425 426 427 428
2017-09-27 Niels Möller <nisse@lysator.liu.se>
Merged armor-signedness branch, starting 2017-08-27.
429 430
2017-09-24 Niels Möller <nisse@lysator.liu.se>
431 432 433 434 435 436 437 438 439 440 441 442 443
* tools/pkcs1-conv.c (base64_decode_in_place): New helper
function.
(decode_base64): Use it.
* sexp-transport-format.c (base64_encode_in_place): New helper
function.
(sexp_transport_vformat): Use it.
* testsuite/base64-test.c (test_fuzz_once): Update to use char
type where appropriate.
(test_main): Use helper functions base64_encode_in_place and
base64_decode_in_place (copied to this file).
444 445 446 447 448
* testsuite/testutils.c (tstring_data): Use uint8_t for data
argument.
* testsuite/testutils.h (SDATA): Use US macro to cast data
argument.
449 450 451 452 453 454 455 456 457 458 459 460 461 462 463 464
2017-08-27 Niels Möller <nisse@lysator.liu.se>
* base64-encode.c (base64_encode_raw, base64_encode_group)
(base64_encode_single, base64_encode_update)
(base64_encode_final): Change type of destination to char *.
* base16-encode.c (base16_encode_single, base16_encode_update):
Likewise.
* base64-decode.c (base64_decode_single, base64_decode_update):
Change type of source argument to const char *. Update (almost)
all callers.
* base16-decode.c (base16_decode_single, base16_decode_update):
Likewise.
* nettle-types.h (nettle_armor_encode_update_func)
(nettle_armor_encode_final_func, nettle_armor_decode_update_func):
Corresponding updates to typedefs.
465 466
2017-09-14 Niels Möller <nisse@lysator.liu.se>
467 468 469
* hkdf.c: Delete unneeded includes. Use Nettle licensing notice.
* hkdf.h: Include only nettle-types.h, not nettle-meta.h.
470 471 472
* ecc-mod.c (ecc_mod): Workaround to silence a false positive from
the clang static analyzer.
473 474 475 476 477 478 479 480
2017-09-12 Niels Möller <nisse@lysator.liu.se>
* testsuite/testutils.h (mpn_zero_p): Avoid redefining mpn_zero_p
when building with mini-gmp. Since the mini-gmp update, this
function is defined by mini-gmp, causing link errors if nettle is
configured with --enable-mini-gmp --disable-shared. Reported by
Tim Rühsen.
481 482 483 484 485 486 487 488 489 490
2017-09-09 Daiki Ueno <dueno@redhat.com>
* testsuite/ecc-mul-g-test.c (test_main): Fixed mpn_cmp call.
* testsuite/ecc-mul-a-test.c (test_main): Likewise.
* eccdata.c (ecc_point_out): Write to given stream, instead of
stderr.
* eccdata.c (output_curve): In curve448, the bit size of the order
is slightly smaller than the one of p's. Adjust ecc_Bmodq_shifted
accordingly.
491 492 493 494 495 496
2017-09-09 Niels Möller <nisse@lysator.liu.se>
* mini-gmp.c: Updated mini-gmp from the gmp repository, latest
change from 2017-07-23.
* mini-gmp.h: Likewise.
497 498 499 500 501
2017-09-06 Niels Möller <nisse@lysator.liu.se>
* hkdf.c (hkdf_expand): Eliminate a (signed) ssize_t variable, use
break rather than return at loop termination.
Niels Möller's avatar
Niels Möller committed
502 503 504 505 506 507 508 509 510 511 512
2017-09-06 Niels Möller <nisse@lysator.liu.se>
HKDF implementation, contributed by Nikos Mavrogiannopoulos.
* hkdf.c (hkdf_extract, hkdf_expand): New file, new functions.
* hkdf.h: New file.
* Makefile.in (nettle_SOURCES): Add hkdf.c.
(HEADERS): Add hkdf.h.
* testsuite/hkdf-test.c: Tests for hkdf-sha256 and hkdf-sha1.
* testsuite/Makefile.in (TS_NETTLE_SOURCES): Added hkdf-test.c.
* nettle.texinfo (Key derivation functions): Document HKDF.
Niels Möller's avatar
Niels Möller committed
513 514 515 516
2017-09-04 Andreas Schneider <asn@samba.org>
* fat-arm.c: Add missing define for _GNU_SOURCE.
517 518 519 520 521 522 523 524 525 526
2017-08-27 Niels Möller <nisse@lysator.liu.se>
* configure.ac (GMP_NUMB_BITS): Set to dummy value "n/a" in
mini-gmp builds.
(NUMB_BITS): New substituted variable which always holds the
configured value.
* Makefile.in (GMP_NUMB_BITS): Renamed variable...
(NUMB_BITS): ...new name
* config.make.in: Update corresponding substitution.
Niels Möller's avatar
Niels Möller committed
527 528 529 530 531
2017-08-26 Niels Möller <nisse@lysator.liu.se>
* ecc-mod-inv.c (ecc_mod_inv): Add missing assert. Fixes a
"dead increment" warning from the clang static analyzer.
532 533
2017-08-26 Niels Möller <nisse@lysator.liu.se>
534 535 536 537
* examples/nettle-openssl.c (struct openssl_cipher_ctx): New
struct. Use everywhere, instead of typing EVP_CIPHER_CTX pointers
directly.
538 539 540 541 542 543 544 545 546 547 548 549 550
* configure.ac: Update openssl-related tests. Checks for
cipher-specific headers are replaced by a check for openssl/evp.h,
and the check for the BF_ecb_encrypt function is replaced by a
check for EVP_CIPHER_CTX_new.
2017-08-03 Daniel P. Berrange <berrange@redhat.com>
* examples/nettle-openssl.c: Rewritten to use openssl's EVP APIs.
The older cipher-specific functions always use openssl's generic
software implementation, while the EVP functions enables
platform-specific code, e.g., using the x86 AES-NI instructions.
(nettle_openssl_init): New function.
Niels Möller's avatar
Niels Möller committed
551 552 553 554 555 556 557
2017-07-18 Niels Möller <nisse@lysator.liu.se>
* ecc-add-eh.c (ecc_add_eh): Fix in-place operation by reordering
two multiplies. Previously, in-place operation resulted in an
invalid call to mpn_mul with overlapping operands. Reported by
Sergei Trofimovich.
558 559 560 561 562 563 564 565 566 567 568 569
2017-06-09 Niels Möller <nisse@lysator.liu.se>
* pss.c (pss_verify_mgf1): Check for m being too large, fixing an
assertion failure for certain invalid signatures. Based on a patch
contributed by Daiki Ueno.
* testsuite/rsa-pss-sign-tr-test.c (test_main): Add test case
contributed by Daiki Ueno. Problem originally found by oss-fuzz,
see https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=2132.
That problem report is currently embargoed, but will hopefully be
public in a month or two.
570 571 572 573 574 575 576 577 578
2017-05-23 Niels Möller <nisse@lysator.liu.se>
Rework the previous change, which had the unintended effect of
always regenerating .test-rules.make after ./configure is run.
* testsuite/Makefile.in (test-rules.stamp): New stamp file target,
depend on Makefile.in, and run $(MAKE) test-rules.
(.test-rules.make): Add a level of indirection, by depending on
test-rules.stamp.
579 580 581 582 583 584 585 586 587 588 589
2017-05-20 Niels Möller <nisse@lysator.liu.se>
* testsuite/Makefile.in (test-rules): Use $(srddir)/-prefix for
.test-rules.make target, and change dependency from Makefile.in to
Makefile.
2017-05-17 Nikos Mavrogiannopoulos <nmav@redhat.com>
* testsuite/Makefile.in: Ensure .test-rules.make is regenerated
when Makefile.in is modified.
590 591
2017-04-09 Niels Möller <nisse@lysator.liu.se>
592 593 594
* testsuite/dlopen-test.c (main): Call dlclose, to fix memory leak
on success.
595 596 597 598 599 600 601
* testsuite/pss-test.c: Delete magic to let valgrind to check if
pss_encode_mgf1 is side-channel silent with respect to the salt
and digest inputs. It turns out that the most significant bits of
the padded bignum, and hence its size, depends on these inputs.
Which results in a data-dependent branch in the normalization code
of at the end of gmp's mpz_import.
602 603
2017-04-04 Niels Möller <nisse@lysator.liu.se>
604
* pss.c (pss_verify_mgf1): Use const for input mpz_t argument.
605
(pss_encode_mgf1): Avoid unnecessary memset and xor operations.
606
607 608 609 610 611 612 613 614 615 616 617 618 619 620 621 622 623 624 625 626 627
Merged RSA-PSS support, contributed by Daiki Ueno.
* pss-mgf1.h, pss.h: New header files.
* pss-mgf1.c (pss_mgf1): New file and function.
* pss.c (pss_encode_mgf1, pss_verify_mgf1): New file and
functions.
* rsa-verify.c (_rsa_verify_recover): New function.
* rsa-pss-sha256-sign-tr.c: (rsa_pss_sha256_sign_digest_tr): New
file and function.
* rsa-pss-sha256-verify.c (rsa_pss_sha256_verify_digest): New
file and function.
* rsa-pss-sha512-sign-tr.c (rsa_pss_sha384_sign_digest_tr)
(rsa_pss_sha512_sign_digest_tr): New file and functions.
* rsa-pss-sha512-verify.c (rsa_pss_sha384_verify_digest)
(rsa_pss_sha512_verify_digest): New file and functions.
* rsa.h: Prototypes for new functions.
* testsuite/rsa-pss-sign-tr-test.c: New test case.
* testsuite/pss-test.c: New test case.
* testsuite/pss-mgf1-test.c: New test case.
* Makefile.in, testsuite/Makefile.in: Added new files.
* nettle.texinfo: Documentation of rsa-pss functions.
628 629
2017-03-20 Niels Möller <nisse@lysator.liu.se>
630 631 632 633
* nettle-internal.h (NETTLE_MAX_HASH_CONTEXT_SIZE): New constant.
* testsuite/meta-hash-test.c (test_main): Add sanity check for
NETTLE_MAX_HASH_CONTEXT_SIZE.
634 635 636
* tools/nettle-hash.c (list_algorithms): Also display the internal
context size.
637 638 639 640 641
2017-01-03 Nikos Mavrogiannopoulos <nmav@redhat.com>
* ecdsa-verify.c (ecdsa_verify): Eliminated memory leak on error
path.
642 643 644 645 646 647 648
2016-10-10 Niels Möller <nisse@lysator.liu.se>
* write-be32.c (_nettle_write_be32): Use const for source argument.
* write-le32.c (_nettle_write_le32): Likewise.
* write-le64.c (_nettle_write_le64): Likewise.
* nettle-write.h: Update prototypes.
Niels Möller's avatar
Niels Möller committed
649 650 651 652
2016-10-01 Niels Möller <nisse@lysator.liu.se>
* Released nettle-3.3.
653 654 655 656 657 658
2016-09-13 Niels Möller <nisse@lysator.liu.se>
* nettle-meta-hashes.c (nettle_hashes): Added SHA3 hashes.
Reported missing by Thomas Walter.
* testsuite/meta-hash-test.c: Update test accordingly.
659 660 661
2016-09-07 Niels Möller <nisse@lysator.liu.se>
* nettle.texinfo (Elliptic curves): Split into sub-nodes.
Niels Möller's avatar
Niels Möller committed
662
(Miscellaneous functions): Document memeql_sec.
Niels Möller's avatar
Niels Möller committed
663
* NEWS: Mention memeql_sec.
664
Niels Möller's avatar
Niels Möller committed
665 666
2016-09-06 Niels Möller <nisse@lysator.liu.se>
Niels Möller's avatar
Niels Möller committed
667 668
* NEWS: Update for 3.3.
Niels Möller's avatar
Niels Möller committed
669 670 671 672
* configure.ac: Bump package version to 3.3.
(LIBNETTLE_MINOR): Bump library version to 6.3.
(LIBHOGWEED_MINOR): Bump library version to 4.3.
673 674 675 676 677 678
2016-09-05 Niels Möller <nisse@lysator.liu.se>
* curve25519.h (NETTLE_CURVE25519_RFC7748): New preprocessor
constant.
* nettle.texinfo: Document it.
679 680
2016-09-03 Niels Möller <nisse@lysator.liu.se>
681 682
* config.make.in (.SUFFIXES): Delete no longer used .p$(OBJEXT).
683 684 685
* sexp.h (TOKEN_CHAR): Delete macro and declaration of
sexp_token_chars. They belong in tools/misc.h, not here.
Niels Möller's avatar
Niels Möller committed
686 687
* examples/ecc-benchmark.c (die): Deleted unused function.
688 689 690 691 692
* testsuite/testutils.h (US): New macro, for unsigned string
literals.
(LDATA): Use the US macro, to eliminate pointer signedness
warnings.
693 694 695 696 697
* testsuite/eddsa-verify-test.c (test_eddsa): Use LDATA.
* testsuite/pbkdf2-test.c (test_main): Likewise.
* testsuite/pkcs1-test.c (test_main): Likewise.
* testsuite/md5-compat-test.c (test_main): Use US macro.
698
699 700 701
* testsuite/sexp-test.c (test_main): Use const char * for assoc
keys. Overlooked in 2016-08-16 change.
702
* testsuite/yarrow-test.c (test_main): Fix pointer
703
signednesss warnings.
704 705
* testsuite/sexp-format-test.c (test_main): Likewise.
* testsuite/rsa-encrypt-test.c (test_main): Likewise.
706
* tools/nettle-lfib-stream.c (main): Likewise.
707
* tools/output.c (sexp_put_string): Likewise.
708
709 710 711 712 713 714
* testsuite/testutils.c (test_armor): Change ascii argument to
const char *.
* testsuite/base16-test.c (test_main): Use LDATA for the non-ascii
argument to test_armor.
* testsuite/base64-test.c (test_main): Likewise.
715 716
* tools/nettle-pbkdf2.c (main): Fix some pointer signedness warning.
* tools/nettle-hash.c (hash_file): Likewise.
717
718 719 720 721 722 723 724 725
* examples/rsa-decrypt.c (process_file): Use memeql_sec to check
the digest.
* memeql-sec.c (memeql_sec): New public function, moved from...
* ccm.c (memeql_sec): ... previous location.
* memops.h: New header file, generalizing memxor.h.
Niels Möller's avatar
Niels Möller committed
726 727 728 729
* testsuite/memeql-test.c (test_main): New test case.
(memeql_sec_for_test): Wrapper to get valgrind to check for
side-channel silence.
730 731 732 733 734
2016-08-29 Niels Möller <nisse@lysator.liu.se>
* sexp-format.c (strlen_u8): New helper function.
(sexp_vformat): Use uint8_t * for strings instead of char *.
735 736
2016-08-16 Niels Möller <nisse@lysator.liu.se>
737 738
* examples/io.c (hash_file): Use uint8_t for buffer.
739 740 741 742
* sexp.c (sexp_iterator_check_type, sexp_iterator_check_types)
(sexp_iterator_assoc): Use const char * for caller's expression
types. Updated all callers.
743 744 745
* rsa2openpgp.c (rsa_keypair_to_openpgp): Added cast to const
uint8_t *.
746 747 748
* pgp-encode.c (write_string): New helper function, replacing...
(WRITE): ... deleted macro.
749 750 751 752 753
* examples/io.c (write_data): Renamed, and use const void * for
the input data. Updated all callers.
(write_string): ... old name.
(write_file): Use const void * for the input data.
754 755
2016-08-05 Niels Möller <nisse@lysator.liu.se>
756
* examples/hogweed-benchmark.c: Use uint8_t for curve25519 values.
Niels Möller's avatar
Niels Möller committed
757
(bench_rsa_init): Use unsigned char for sexp strings.
Niels Möller's avatar
Niels Möller committed
758
(bench_dsa_init): Likewise.
759 760
(hash_string): Delete length argument, calling strlen instead.
Cast string to const uint8_t *. Updated callers.
Niels Möller's avatar
Niels Möller committed
761
762 763 764
* examples/io.c (read_file): Use size_t for sizes, and uint8_t for
the contents.
765 766
2016-08-04 Niels Möller <nisse@lysator.liu.se>
767 768 769
* dsa-sign.c (dsa_sign): Return failure if p is even, so that an
invalid key doesn't result in a crash inside mpz_powm_sec.
770 771 772 773 774 775
* rsa-sign-tr.c (rsa_compute_root_tr): Return failure if any of p,
q or n is even, to avoid crashing inside mpz_powm_sec. Invalid
keys with even modulo are rejected by rsa_public_key_prepare and
rsa_private_key_prepare, but some applications, notably gnutls,
don't use them.
776 777 778 779 780 781
2016-07-31 Niels Möller <nisse@lysator.liu.se>
* rsa.c (_rsa_check_size): Check that n is odd. Otherwise, using
an invalid key may crash in mpz_powm_sec. Problem reported by
Hanno Böck.
782 783 784 785 786 787 788 789 790 791
2016-07-13 Niels Möller <nisse@lysator.liu.se>
* bignum.c (nettle_mpz_from_octets): Unconditionally use
mpz_import.
* gmp-glue.c (mpn_copyd, mpn_copyi, mpn_zero): Deleted
compatibility definitions for older versions of GMP.
* gmp-glue.h (mpn_sqr): Deleted compatibility definition.
* testsuite/testutils.c (mpz_combit): Deleted compatibility
definition.
Niels Möller's avatar
Niels Möller committed
792 793 794 795 796 797 798 799 800 801 802
2016-07-12 Niels Möller <nisse@lysator.liu.se>
* configure.ac: Check for mpz_powm_sec, and require GMP-5.0 or
later.
* bignum.h (mpz_powm_sec): Fall back to plain mpz_powm for
mini-gmp build.
* dsa-sign.c (dsa_sign): Use mpz_powm_sec.
* rsa-sign.c (rsa_compute_root): Likewise.
* rsa-sign-tr.c (rsa_blind, rsa_compute_root_tr): Likewise.
* rsa-blind.c (_rsa_blind): Likewise.
803 804
2016-05-02 Niels Möller <nisse@lysator.liu.se>
805 806
* nettle.texinfo: Update Curve25519 documentation.
807 808 809
* testsuite/curve25519-dh-test.c: Test that inputs bits which must
be ignored really are ignored.
810 811 812
2016-04-25 Niels Möller <nisse@lysator.liu.se>
* curve25519-mul.c (curve25519_mul): Ignore top bit of the input x
813
coordinate, as required by RFC 7748.
814
Niels Möller's avatar
Niels Möller committed
815 816 817 818 819 820
2016-03-30 Niels Möller <nisse@lysator.liu.se>
From Nikos Mavrogiannopoulos.
* configure.ac: Change dll names to follow the libtool convention
with only major version number in the name.
Niels Möller's avatar
Niels Möller committed
821 822
2016-03-15 Niels Möller <nisse@lysator.liu.se>
Niels Möller's avatar
Niels Möller committed
823 824 825 826 827 828
* twofish.c (gf_multiply): Change return value to uint32_t, to
make shifting of the return value well defined, without any type
casts. Fixes an undefined shift in compute_s, reported by Nikos
Mavrogiannopoulos.
(h_byte): Deleted type casts.
829 830 831 832
* blowfish.c (blowfish_encrypt, blowfish_decrypt): Use READ_UINT32
macro. Fixes an undefined shift, reported by Nikos
Mavrogiannopoulos.
Niels Möller's avatar
Niels Möller committed
833 834 835 836 837 838
From Nikos Mavrogiannopoulos.
* configure.ac (HOGWEED_EXTRA_SYMBOLS): Add "mp_*", when building
with mini-gmp.
* des.c (des_weak_p): Check that the hash value is in the proper
range before using it. Fixes an out-of-bounds read.
839 840 841 842 843
2016-03-14 Niels Möller <nisse@lysator.liu.se>
* getopt.c (_getopt_internal_r): Fix c99-ism, move declarations to
top of block. Reported by Henrik Grubbström.
844 845
2016-02-16 Niels Möller <nisse@lysator.liu.se>
846 847 848 849 850
* tools/input.c (sexp_get_string_length): Process advanced string
syntax only when in advanced mode. Fixes an assertion failure
reported by Hanno Böck, for input where advanced syntax is
improperly wrapped inside transport syntax.
851 852 853 854 855
* tools/parse.c (sexp_parse): Fail with an error message for
unexpected ']' characters. Fixes crash reported by Hanno Böck.
Also handle SEXP_DISPLAY (internal error) explicitly, without a
default clause.
856 857 858 859
2016-01-28 Niels Möller <nisse@lysator.liu.se>
* Released nettle-3.2.
860 861 862 863 864 865 866 867
2016-01-26 Niels Möller <nisse@lysator.liu.se>
* tools/nettle-pbkdf2.c (main): Fix handling of unrecognized
options. Bug reported by Dongsheng Zhang. Display usage message
and exit non-zero. Also added "Usage: "-prefix to the message.
* tools/nettle-hash.c (usage): New function, extracted from main.
(main): Analogous fix for unrecognized options.
868 869 870 871
2016-01-23 Niels Möller <nisse@lysator.liu.se>
* nettle.texinfo: Set UPDATED-FOR to 3.2.
Niels Möller's avatar
Niels Möller committed
872 873 874 875 876
2016-01-21 Niels Möller <nisse@lysator.liu.se>
* .gitlab-ci.yml: New file. Configuration for gitlab's continuous
integration system.
877 878
2016-01-20 Niels Möller <nisse@lysator.liu.se>
879 880
* testsuite/dlopen-test.c (main): Mark arguments as UNUSED.
881 882
* testsuite/Makefile.in (clean): Delete dlopen-test.
Niels Möller's avatar
Niels Möller committed
883 884 885 886
* configure.ac: Bump package version, to nettle-3.2.
(LIBNETTLE_MINOR, LIBHOGWEED_MINOR): Bump minor versions, to
libnettle.so.6.2 and and libhogweed.so.4.2.
Niels Möller's avatar
Niels Möller committed
887 888
2016-01-10 Niels Möller <nisse@lysator.liu.se>
889 890 891
* base64-encode.c (encode_raw): Use const uint8_t * for the
alphabet argument.
Niels Möller's avatar
Niels Möller committed
892 893 894
* nettle.texinfo (RSA): Document the rsa_pkcs1_verify and
rsa_pkcs1_sign functions, and the new rsa_*_tr functions.
895 896
2015-12-18 Niels Möller <nisse@lysator.liu.se>
897 898 899 900 901
* testsuite/testutils.h: Fix include order, system headers before
nettle headers. Always include version.h, needed by
version-test.c. It was included indirectly via bignum.h, but only
if configured with publickey support.
902 903
* configure.ac (IF_DLOPEN_TEST): Fixed shell conditional.
904 905 906
* testsuite/ecc-mod-test.c (test_main): Handle random seeding if
NETTLE_TEST_SEED is set in the environment.
907 908 909 910 911 912 913 914
2015-12-15 Niels Möller <nisse@lysator.liu.se>
* x86_64/ecc-384-modp.asm: Fixed carry propagation bug. Problem
reported by Hanno Böck. Simplified the folding to always use
non-negative carry, the old code attempted to add in a carry which
could be either positive or negative, but didn't get that case
right.
915 916 917 918 919 920
2015-12-10 Niels Möller <nisse@lysator.liu.se>
* ecc-256.c (ecc_256_modp): Fixed carry propagation bug. Problem
reported by Hanno Böck.
(ecc_256_modq): Fixed another carry propagation bug.
921 922 923 924 925
2015-11-23 Niels Möller <nisse@lysator.liu.se>
* nettle.texinfo: Document rsa_encrypt, rsa_decrypt and
rsa_decrypt_tr. Text contributed by Andy Lawrence.
926 927 928 929
2015-11-15 Niels Möller <nisse@lysator.liu.se>
* rsa.h (_rsa_blind, _rsa_unblind): Mark as deprecated.
930 931 932 933 934 935 936 937 938 939 940 941 942
2015-09-17 Niels Möller <nisse@lysator.liu.se>
* rsa-md5-sign-tr.c (rsa_md5_sign_tr, rsa_md5_sign_digest_tr): New
file, new functions.
* rsa-sha1-sign-tr.c (rsa_sha1_sign_tr, rsa_sha1_sign_digest_tr):
Likewise.
* rsa-sha256-sign-tr.c (rsa_sha256_sign_tr)
(rsa_sha256_sign_digest_tr): Likewise.
* rsa-sha512-sign-tr.c (rsa_sha512_sign_tr)
(rsa_sha512_sign_digest_tr): Likewise.
* rsa.h: Added corresponding prototypes.
* Makefile.in (hogweed_SOURCES): Added new files.
943 944 945
* testsuite/testutils.c (SIGN): Extend macro to test new
functions, and the rsa_*_sign_digest functions. Updated callers.
946 947
2015-09-14 Niels Möller <nisse@lysator.liu.se>
948 949 950 951 952 953 954
* rsa-decrypt-tr.c (rsa_decrypt_tr): Use rsa_compute_root_tr.
Mainly for simplicity and consistency, I'm not aware of any CRT
fault attacks on RSA decryption.
* testsuite/rsa-encrypt-test.c (test_main): Added test with
invalid private key.
955 956 957 958 959 960 961 962
* rsa-sign-tr.c (rsa_compute_root_tr): New file and function.
* rsa.h: Declare it.
* rsa-pkcs1-sign-tr.c (rsa_pkcs1_sign_tr): Use rsa_compute_root_tr.
(rsa_verify_res): Deleted, replaced by rsa_compute_root_tr.
* testsuite/rsa-sign-tr-test.c (test_rsa_sign_tr): Check that
signature argument is unchanged on failure.
* Makefile.in (hogweed_SOURCES): Added rsa-sign-tr.c.
963 964
2015-09-07 Niels Möller <nisse@lysator.liu.se>
Niels Möller's avatar
Niels Möller committed
965 966 967
* testsuite/rsa-sign-tr-test.c: Drop include of nettle-internal.h.
(test_main): Fix incorrect use of sizeof, and use LDATA macro.
968 969 970 971 972 973 974
From Nikos Mavrogiannopoulos.
* rsa-pkcs1-sign-tr.c (rsa_verify_res): New function.
(rsa_pkcs1_sign_tr): Check result of private key operation, to
protect against hardware or software errors leaking the private
key.
* testsuite/rsa-sign-tr-test.c: New testcase.
Niels Möller's avatar
Niels Möller committed
975 976 977 978
2015-09-06 Niels Möller <nisse@lysator.liu.se>
* nettle.texinfo: Updated SHA3 documentation.
Niels Möller's avatar
Niels Möller committed
979 980
2015-09-02 Niels Möller <nisse@lysator.liu.se>
981 982 983 984 985 986 987 988 989 990 991 992
* testsuite/dlopen-test.c: New test program, exposing the problem
with ifunc and RTLD_NOW.
* testsuite/Makefile.in (TS_ALL): Conditionally add dlopen-test.
(SOURCES): Added dlopen-test.c.
(dlopen-test): New target, unlike other test programs, *not*
linked with -lnettle.
* configure.ac: Check for dlfcn.h and the dlopen function.
(IF_DLOPEN_TEST): New substituted variable, true if dlopen is
available and we are building a shared library.
Niels Möller's avatar
Niels Möller committed
993 994 995
* fat-setup.h: Disable use of ifunc, since it breaks dlopen with
RTLD_NOW.
996 997
2015-08-25 Niels Möller <nisse@lysator.liu.se>
998 999
* NEWS: Started on entries for Nettle-3.2.
1000 1001
* sha3.h (NETTLE_SHA3_FIPS202): New preprocessor constant.
1002 1003 1004 1005 1006 1007 1008 1009 1010 1011 1012
2015-08-24 Niels Möller <nisse@lysator.liu.se>
* testsuite/sha3.awk: Document origin of test vectors.
From Nikos Mavrogiannopoulos.
* sha3.c (_sha3_pad): Update for NIST version.
* testsuite/sha3-224-test.c: Updated test vectors.
* testsuite/sha3-256-test.c: Likewise.
* testsuite/sha3-384-test.c: Likewise.
* testsuite/sha3-512-test.c: Likewise.
1013 1014 1015 1016 1017
2015-06-03 Niels Möller <nisse@lysator.liu.se>
* arm/neon/chacha-core-internal.asm: New file. 55% speedup over C
version on Cortex-A9.
1018 1019 1020 1021 1022
2015-05-19 Niels Möller <nisse@lysator.liu.se>
* configure.ac: ABI detection (n32 or n64) on Irix, and
appropriate default for libdir. Patch from Klaus Ziegler.
1023 1024 1025 1026 1027 1028 1029 1030 1031
2015-05-12 Niels Möller <nisse@lysator.liu.se>
* version.c (nettle_version_major, nettle_version_minor): New
file. New functions, returning the value of the corresponding
preprocessor constant.
* Makefile.in (nettle_SOURCES): Added version.c.
* testsuite/version-test.c: New testcase.
* testsuite/Makefile.in (TS_NETTLE_SOURCES): Added version-test.c.
1032 1033
2015-04-29 Niels Möller <nisse@lysator.liu.se>
1034 1035
* arm/v6/sha256-compress.asm: Fix syntax error in offset
addressing. Spotted by Jukka Ukkonen.
1036 1037 1038
* arm/v6/aes-decrypt-internal.asm: Drop %-prefix on r12 register.
* arm/v6/aes-encrypt-internal.asm: Likewise.
Niels Möller's avatar
Niels Möller committed
1039 1040
2015-04-24 Niels Möller <nisse@lysator.liu.se>
Niels Möller's avatar
Niels Möller committed
1041 1042
* Released nettle-3.1.1.
Niels Möller's avatar
Niels Möller committed
1043 1044 1045 1046
* configure.ac: Bump package version, to nettle-3.1.1.
(LIBNETTLE_MINOR, LIBHOGWEED_MINOR): Bump minor versions, to
libnettle.so.6.1 and and libhogweed.so.4.1.
1047 1048 1049 1050 1051
2015-04-22 Niels Möller <nisse@lysator.liu.se>
* x86_64/gcm-hash8.asm: Use ".value" instead of ".short", since
the latter is not supported by the Sun/Oracle assembler.
1052 1053 1054 1055 1056
2015-04-13 Niels Möller <nisse@lysator.liu.se>
* configure.ac: Fix shell quoting in test of GMP_NUMB_BITS asm
compatibility. Reported by Edward Sheldrake.
1057 1058 1059 1060
2015-04-07 Niels Möller <nisse@lysator.liu.se>
* Released nettle-3.1.
1061
2015-03-31 Niels Möller <nisse@lysator.liu.se>
1062
1063 1064 1065 1066 1067 1068 1069
* x86_64/ecc-224-modp.asm: Require that GMP_NUMB_BITS == 64.
* x86_64/ecc-521-modp.asm: Likewise. Note that the other
ecc-*-modp.asm files happen to work fine on x86_64, with either 32
or 64 bits.
* asm.m4 (GMP_NUMB_BITS): New macro, expanding to nothing.
1070 1071
* configure.ac: Move tests for compiler characteristics,
libraries, and GMP_NUMB_BITS, before assembler-related tests.
1072 1073 1074
For files in $asm_hogweed_optional_list, check if they declare
a GMP_NUMB_BITS requirement, and skip files which are incompatible
with the configuration. Needed for --enable-mini-gmp om w64.
1075
1076 1077 1078
* Makefile.in (clean-here): Unconditionally delete *.a (including
stub libraries like *.dll.a).
1079
2015-03-30 Niels Möller <nisse@lysator.liu.se>
1080
1081 1082 1083 1084
* version.h.in (GMP_NUMB_BITS) [NETTLE_USE_MINI_GMP]: Move
definition here (uses configure substitution).
* bignum.h (GMP_NUMB_BITS): ...old location.
Niels Möller's avatar
Niels Möller committed
1085 1086 1087
* nettle.texinfo: Updated version number.
(Installation): Document some more configure options.
1088
* testsuite/symbols-test: Look for NETTLE_USE_MINI_GMP in
1089 1090
version.h, not bignum.h. Allow leading underscore on mini-gmp
symbols.
1091
1092
2015-03-26 Niels Möller <nisse@lysator.liu.se>
1093
1094 1095 1096 1097 1098 1099 1100 1101 1102 1103 1104 1105 1106
* Makefile.in (PRE_CPPFLAGS): Drop -I$(srcdir), no longer needed.
(HEADERS): Added bignum.h. Removed version.h.
(INSTALL_HEADERS): Added version.h.
(DISTFILES): Removed bignum.h.in.
(bignum.h): Deleted make target.
(distclean-here): Don't delete bignum.h.
* configure.ac: No longer generate bignum.h.
* bignum.h: Renamed. Removed substitution of NETTLE_USE_MINI_GMP,
and include version.h instead.
* bignum.h.in: ... old name.
1107 1108
* version.h.in (NETTLE_USE_MINI_GMP): Substitute here.
1109
2015-03-25 Niels Möller <nisse@lysator.liu.se>
1110
1111 1112 1113
* configure.ac (MAJOR_VERSION, MINOR_VERSION): Tweak sed
expressions, to tolerate version suffixes.
1114 1115 1116
* Makefile.in (distdir): Include assembly files from the new
x86_64/aesni, x86_64/fat, and arm/fat directories.
1117 1118 1119
* ed25519-sha512-pubkey.c: Fix stack overwrite. The digest array
must have room for a complete sha512 digest.
1120
2015-03-19 Niels Möller <nisse@lysator.liu.se>
1121
1122 1123 1124 1125 1126 1127 1128 1129 1130
* Makefile.in (OPT_HOGWEED_SOURCES): Deleted make variable.
(nettle_SOURCES, hogweed_SOURCES): Don't include optional sources
here.
(OPT_SOURCES): New variable.
(SOURCES): Include OPT_SOURCES.
(DISTFILES): Drop mini-gmp.c here, included via OPT_SOURCES.
(nettle_OBJS, hogweed_OBJS): Add the object files corresponding to
the optional source files included in the build.
1131 1132 1133 1134
* ecc-curve.h (nettle_curve25519): Removed public declaration.
* ecc-internal.h (_nettle_curve25519): New location, new name.
Updated all users.
Niels Möller's avatar
Niels Möller committed
1135 1136
* nettle.texinfo: Updated EdDSA documentation.
1137 1138 1139 1140 1141 1142
* Makefile.in (DISTFILES): Added version.h.in, libnettle.map.in,
and libhogweed.map.in (latter two patch by Nikos).
(version.h): New make target.
(distclean-here): Added version.h, libnettle.map, and
libhogweed.map.
1143 1144 1145 1146 1147
From Nikos Mavrogiannopoulos.
* configure.ac (MAJOR_VERSION, MINOR_VERSION): New substituted
variables.
* version.h.in: New file, defining version numbers.
1148
2015-03-18 Niels Möller <nisse@lysator.liu.se>
1149
1150 1151 1152 1153 1154 1155
EdDSA interface change, use plain strings to represent keys.
* eddsa.h (_ED25519_LIMB_SIZE): Deleted constant.
(struct ed25519_private_key, ed25519_public_key): Deleted.
* eddsa-expand.c (_eddsa_expand_key): Don't compute the public
key.
(_eddsa_expand_key_itch): Deleted function.
1156 1157
* eddsa-pubkey.c (_eddsa_public_key, _eddsa_public_key_itch): New
file, new functions.
1158 1159 1160 1161 1162 1163 1164 1165 1166 1167 1168 1169 1170 1171
* ed25519-sha512-pubkey.c (ed25519_sha512_public_key): New file
and function.
* ed25519-sha512-verify.c (ed25519_sha512_set_public_key): Deleted
function.
(ed25519_sha512_verify): Use a string to represent the public key.
* ed25519-sha512-sign.c (ed25519_sha512_set_private_key): Deleted
function.
(ed25519_sha512_sign): Use strings for the input key pair.
* Makefile.in (hogweed_SOURCES): Added eddsa-pubkey.c and
ed25519-sha512-pubkey.c.
* testsuite/eddsa-sign-test.c (test_eddsa_sign): Adapt to
_eddsa_expand_key changes, and use _eddsa_public_key.
* testsuite/ed25519-test.c (test_one): Test
ed25519_sha512_public_key, and adapt to new ed25519 interface.
1172
1173
2015-03-14 Niels Möller <nisse@lysator.liu.se>
Niels Möller's avatar
Niels Möller committed
1174 1175 1176 1177 1178
* ccm.c (memeql_sec): New function, more side-channel silent than
memcmp.
(ccm_decrypt_message): Use it.
1179
2015-03-12 Niels Möller <nisse@lysator.liu.se>
Niels Möller's avatar
Niels Möller committed
1180
1181 1182 1183 1184 1185
* base64.h (struct base64_encode_ctx): Micro optimization of
struct layout, saving a few bytes.
(struct base64_decode_ctx): Likewise.
* base16.h (struct base16_decode_ctx): Likewise.
Niels Möller's avatar
Niels Möller committed
1186 1187
* nettle.texinfo (ASCII encoding): Document base64url functions.
1188
2015-03-10 Niels Möller <nisse@lysator.liu.se>
1189
1190 1191 1192 1193
* nettle.texinfo: Update documentation of curve25519_mul. Say that
the output is undefined for points belonging to the twist rather
than the proper curve.
1194
* curve25519-mul.c (curve25519_mul): Changed return type to void.
1195
* curve25519.h (curve25519_mul): Updated prototype.
1196 1197 1198 1199
* examples/hogweed-benchmark.c (bench_curve25519_mul): Drop check
of curve25519_mul return value.
* testsuite/curve25519-dh-test.c (test_a): Likewise.
1200
2015-02-26 Niels Möller <nisse@lysator.liu.se>
1201 1202 1203
* nettle.texinfo: Document curve25519 and eddsa.
1204 1205
2015-02-10 Niels Möller <nisse@lysator.liu.se>
1206 1207 1208 1209 1210 1211 1212 1213
* base64url-meta.c (nettle_base64url): New file.
* nettle-meta.h (nettle_base64url): Declare it.
* nettle-meta-armors.c (nettle_armors): Added nettle_base64url.
* testsuite/meta-armor-test.c: Updated testcase.
* testsuite/base64-test.c (test_main): Additional tests, using
nettle_base64url.
* Makefile.in (nettle_SOURCES): Added base64url-meta.c.
1214 1215 1216 1217 1218 1219 1220 1221 1222 1223 1224 1225
Base-64 generalization to support RFC4648 URL safe alphabet,
contributed by Amos Jeffries.
* base64url-decode.c (base64url_decode_init): New file and
function.
* base64url-encode.c (base64url_encode_init): New file and
function.
* Makefile.in (nettle_SOURCES): Added base64url-encode.c and
base64url-decode.c.
* base64.h: Declare new functions.
* testsuite/base64-test.c (test_fuzz): Test base64url encoding and
decoding.
1226 1227 1228 1229 1230 1231 1232 1233 1234 1235 1236 1237 1238 1239
* base64.h (struct base64_encode_ctx): Added pointer to alphabet.
(struct base64_decode_ctx): Added pointer to decoding table.
* base64-decode.c (base64_decode_init): Initialize table pointer.
Moved definition of table to local scope.
(base64_decode_single): Use the context's decoding table.
* base64-encode.c (ENCODE): Added alphabet argument. Updated all
uses.
(encode_raw): New static function, like base64_encode_raw
but with an alphabet argument.
(base64_encode_raw): Call encode_raw.
(base64_encode_init): Initialize alphabet pointer.
(base64_encode_single, base64_encode_update, base64_encode_final):
Use the context's alphabet.
1240 1241
2015-02-09 Niels Möller <nisse@lysator.liu.se>
1242 1243 1244
* base64-encode.c (base64_encode): Deleted old #if:ed out
function.
1245 1246 1247
* testsuite/base64-test.c (test_fuzz_once, test_fuzz): Additional
tests, based on contribution by Amos Jeffries.
1248 1249 1250
2015-02-05 Niels Möller <nisse@lysator.liu.se>
* configure.ac (LIBHOGWEED_MAJOR): Undo latest bump, 4 should be
1251
enough (previous release, nettle-3.0, used 3).
1252
1253 1254
2015-01-30 Niels Möller <nisse@lysator.liu.se>
1255 1256 1257 1258 1259 1260 1261 1262 1263 1264
Update chacha-poly1305 for draft-irtf-cfrg-chacha20-poly1305-08.
* chacha-poly1305.h (CHACHA_POLY1305_NONCE_SIZE): Increase to 12
bytes, i.e., CHACHA_NONCE96_SIZE.
* chacha-poly1305.c (chacha_poly1305_set_nonce): Use
chacha_set_nonce96.
(poly1305_pad): New function.
(chacha_poly1305_encrypt): Use poly1305_pad.
(chacha_poly1305_digest): Call poly1305_pad, and format length
fields as a single poly1305 block.
1265 1266 1267 1268
* chacha-set-nonce.c (chacha_set_nonce96): New function.
* chacha.h (CHACHA_NONCE96_SIZE): New constant.
* testsuite/chacha-test.c: Add test for chacha with 96-bit nonce.
1269 1270 1271 1272 1273 1274 1275 1276 1277 1278 1279 1280 1281 1282 1283 1284 1285 1286 1287 1288 1289 1290 1291 1292 1293
2015-01-27 Niels Möller <nisse@lysator.liu.se>
* ecc.h: Deleted declarations of unused itch functions. Moved
declarations of internal functions to...
* ecc-internal.h: ...new location. Also added a leading under
score on the symbols.
(ecc_a_to_j, ecc_j_to_a, ecc_eh_to_a, ecc_dup_jj, ecc_add_jja)
(ecc_add_jjj, ecc_dup_eh, ecc_add_eh, ecc_add_ehh, ecc_mul_g)
(ecc_mul_a, ecc_mul_g_eh, ecc_mul_a_eh): Affected functions.
2015-01-26 Niels Möller <nisse@lysator.liu.se>
* ecc-add-eh.c (ecc_add_eh_itch): Deleted.
* ecc-add-ehh.c (ecc_add_ehh_itch): Deleted.
* ecc-add-jja.c (ecc_add_jja_itch): Deleted.
* ecc-add-jjj.c (ecc_add_jjj_itch): Deleted.
* ecc-dup-eh.c (ecc_dup_eh_itch): Deleted.
* ecc-dup-jj.c (ecc_dup_jj_itch): Deleted.
* ecc-eh-to-a.c (ecc_eh_to_a_itch): Deleted.
* ecc-j-to-a.c (ecc_j_to_a_itch): Deleted.
* ecc-mul-a-eh.c (ecc_mul_a_eh_itch): Deleted.
* ecc-mul-a.c (ecc_mul_a_itch): Deleted.
* ecc-mul-g-eh.c (ecc_mul_g_eh_itch): Deleted.
* ecc-mul-g.c (ecc_mul_g_itch): Deleted.
1294 1295
2015-01-25 Niels Möller <nisse@lysator.liu.se>
1296 1297 1298 1299 1300
* arm/fat/sha1-compress-2.asm: New file.
* arm/fat/sha256-compress-2.asm: Likewise.
* fat-arm.c (fat_init): Setup for use of additional v6 assembly
functions.
1301 1302 1303 1304 1305 1306 1307 1308 1309 1310
* sha1-compress.c: Prepare for fat build with C and assembly
implementations.
* sha256-compress.c: Likewise.
* fat-setup.h (sha1_compress_func, sha256_compress_func): New typedefs.
* configure.ac (asm_nettle_optional_list): Added
sha1-compress-2.asm and sha256-compress-2.asm, and corresponding
HAVE_NATIVE_*.
1311 1312 1313 1314 1315
From Martin Storsjö:
* arm: Add .arch directives for armv6. This allows building these
files as part of a fat build, even if the assembler by default
targets a lower architecture version.
1316 1317 1318 1319 1320 1321 1322 1323 1324 1325
2015-01-23 Niels Möller <nisse@lysator.liu.se>
* fat-setup.h (DEFINE_FAT_FUNC): Check value of function pointer,
before calling fat_init. Should be correct even without memory
barrier.
* fat-x86_64.c (fat_init): Deleted static variable initialized.
The checks of the relevant pointer in DEFINE_FAT_FUNC is more
robust.
* fat-arm.c (fat_init): Likewise.
1326 1327
2015-01-21 Niels Möller <nisse@lysator.liu.se>
Niels Möller's avatar
Niels Möller committed
1328 1329 1330 1331 1332 1333 1334 1335
* fat-arm.c (fat_init): Setup for use of neon assembly functions.
* arm/fat/salsa20-core-internal-2.asm: New file.
* arm/fat/sha3-permute-2.asm: New file.
* arm/fat/sha512-compress-2.asm: New file.
* arm/fat/umac-nh-2.asm: New file.
* arm/fat/umac-nh-n-2.asm: New file.
1336 1337 1338 1339 1340 1341 1342 1343 1344 1345 1346
* salsa20-core-internal.c: Prepare for fat build with C and
assembly implementations.
* sha512-compress.c: Likewise.
* sha3-permute.c: Likewise.
* umac-nh.c: Likewise.
* umac-nh-n.c: Likewise.
* configure.ac (asm_nettle_optional_list): Added more *-2.asm
files, and corresponding HAVE_NATIVE_* defines. Recognize PROLOGUE
macro in asm files, also when not at the start of the line.
1347 1348
2015-01-20 Niels Möller <nisse@lysator.liu.se>
1349 1350 1351
* fat-arm.c (get_arm_features): Check NETTLE_FAT_OVERRIDE
environment variable.
1352 1353 1354 1355 1356 1357 1358 1359
* fat-x86_64.c (get_x86_features): New function. Check
NETTLE_FAT_OVERRIDE environment variable.
(fat_init): Use it.
* fat-setup.h (secure_getenv) [!HAVE_SECURE_GETENV]: Dummy
definition, returning NULL.
(ENV_OVERRIDE): New constant.
1360 1361
* configure.ac: Check for secure_getenv function.
1362 1363
2015-01-19 Niels Möller <nisse@lysator.liu.se>
1364 1365 1366 1367 1368 1369 1370
* configure.ac: Fat library setup for arm.
* fat-arm.c: New file.
* arm/fat/aes-encrypt-internal.asm: New files.
* arm/fat/aes-encrypt-internal-2.asm: New file.
* arm/fat/aes-decrypt-internal.asm: New file.
* arm/fat/aes-decrypt-internal-2.asm: New file.
1371 1372 1373 1374 1375
* Makefile.in (DISTFILES): Added fat-setup.h.
* fat-setup.h: New file, declarations moved from...
* fat-x86_64.c: ... old location
1376 1377
|
{
"url": "https://git.lysator.liu.se/nettle/nettle/-/blame/0355cfad41931c5583e391bfcd2deb806a6d7f5e/ChangeLog",
"source_domain": "git.lysator.liu.se",
"snapshot_id": "crawl=CC-MAIN-2021-31",
"warc_metadata": {
"Content-Length": "1049451",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:5QH2JVKYFXZKCVRGKWIMMRDU3HCQUBGD",
"WARC-Concurrent-To": "<urn:uuid:73f16099-64d2-4320-a6c1-6df2d804b24d>",
"WARC-Date": "2021-07-27T06:47:00Z",
"WARC-IP-Address": "130.236.254.118",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:BKAQTRB4RDRLSG33GSDDQGI6ENT3JNRB",
"WARC-Record-ID": "<urn:uuid:28bbb8b9-78c8-4881-8963-af9e549c7443>",
"WARC-Target-URI": "https://git.lysator.liu.se/nettle/nettle/-/blame/0355cfad41931c5583e391bfcd2deb806a6d7f5e/ChangeLog",
"WARC-Truncated": "length",
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:d41a7cc2-56e5-431c-a660-50f5471a90d2>"
},
"warc_info": "isPartOf: CC-MAIN-2021-31\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for July/August 2021\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-86.ec2.internal\r\nsoftware: Apache Nutch 1.18 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.2-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
17,
29,
51,
74,
78,
127,
128,
134,
199,
258,
259,
281,
304,
308,
376,
397,
401,
435,
488,
510,
533,
536,
537,
555,
604,
605,
669,
741,
786,
787,
809,
832,
904,
953,
954,
985,
1053,
1121,
1185,
1210,
1278,
1286,
1349,
1374,
1375,
1431,
1492,
1549,
1611,
1645,
1692,
1693,
1759,
1826,
1873,
1913,
1914,
1920,
1969,
1970,
1979,
2046,
2075,
2076,
2088,
2150,
2211,
2228,
2229,
2274,
2323,
2324,
2346,
2426,
2474,
2512,
2555,
2585,
2633,
2682,
2717,
2756,
2797,
2848,
2849,
2894,
2943,
2944,
3008,
3075,
3142,
3198,
3265,
3308,
3309,
3375,
3440,
3508,
3576,
3586,
3587,
3609,
3632,
3638,
3687,
3688,
3697,
3749,
3815,
3816,
3838,
3861,
3870,
3937,
3965,
3966,
4022,
4071,
4138,
4204,
4227,
4293,
4355,
4420,
4486,
4553,
4620,
4680,
4748,
4814,
4861,
4927,
4994,
4995,
5015,
5064,
5065,
5131,
5144,
5145,
5173,
5222,
5223,
5268,
5315,
5383,
5420,
5421,
5441,
5490,
5491,
5561,
5576,
5577,
5593,
5642,
5643,
5711,
5712,
5764,
5813,
5814,
5862,
5914,
5968,
5969,
6031,
6057,
6109,
6110,
6159,
6160,
6215,
6299,
6300,
6323,
6344,
6375,
6431,
6475,
6534,
6582,
6641,
6689,
6764,
6790,
6791,
6828,
6891,
6892,
6950,
6967,
6968,
7002,
7003,
7011,
7060,
7061,
7065,
7117,
7121,
7176,
7184,
7235,
7293,
7313,
7369,
7410,
7466,
7493,
7494,
7542,
7591,
7592,
7659,
7690,
7749,
7809,
7869,
7880,
7881,
7942,
7978,
7979,
8003,
8052,
8053,
8124,
8188,
8217,
8218,
8240,
8263,
8283,
8343,
8344,
8410,
8427,
8428,
8472,
8532,
8533,
8598,
8618,
8675,
8741,
8815,
8865,
8933,
8945,
8946,
8954,
9003,
9004,
9016,
9059,
9123,
9151,
9155,
9156,
9172,
9221,
9222,
9281,
9282,
9310,
9359,
9360,
9403,
9448,
9516,
9551,
9552,
9560,
9609,
9610,
9622,
9690,
9705,
9706,
9722,
9786,
9787,
9851,
9852,
9876,
9931,
9932,
9994,
10056,
10116,
10117,
10189,
10238,
10239,
10297,
10358,
10426,
10494,
10561,
10572,
10628,
10673,
10732,
10733,
10786,
10831,
10832,
10880,
10916,
10917,
10933,
10982,
10983,
11040,
11041,
11077,
11120,
11121,
11188,
11256,
11264,
11313,
11381,
11404,
11405,
11427,
11450,
11470,
11519,
11520,
11588,
11658,
11659,
11681,
11704,
11740,
11789,
11790,
11845,
11899,
11923,
11966,
12011,
12060,
12061,
12077,
12126,
12127,
12195,
12196,
12218,
12241,
12277,
12326,
12327,
12392,
12408,
12409,
12473,
12532,
12552,
12553,
12561,
12610,
12611,
12639,
12705,
12729,
12789,
12843,
12866,
12915,
12916,
12924,
12986,
12987,
12999,
13052,
13088,
13089,
13111,
13134,
13142,
13195,
13196,
13212,
13278,
13338,
13398,
13399,
13411,
13476,
13530,
13531,
13551,
13617,
13649,
13683,
13750,
13751,
13773,
13796,
13824,
13873,
13874,
13938,
14004,
14011,
14063,
14064,
14086,
14109,
14117,
14166,
14167,
14171,
14195,
14217,
14240,
14244,
14245,
14269,
14318,
14319,
14381,
14441,
14471,
14472,
14494,
14517,
14549,
14598,
14599,
14665,
14721,
14784,
14844,
14855,
14856,
14896,
14945,
14946,
15000,
15067,
15134,
15195,
15262,
15324,
15356,
15357,
15379,
15402,
15426,
15475,
15476,
15521,
15570,
15620,
15621,
15643,
15666,
15690,
15739,
15740,
15807,
15858,
15912,
15913,
15921,
15970,
15971,
15993,
16016,
16020,
16062,
16066,
16067,
16075,
16124,
16125,
16157,
16219,
16267,
16331,
16357,
16416,
16478,
16515,
16516,
16524,
16592,
16645,
16649,
16650,
16672,
16695,
16699,
16760,
16764,
16765,
16787,
16810,
16814,
16871,
16893,
16916,
16920,
16921,
16943,
16966,
16970,
17029,
17033,
17034,
17042,
17091,
17092,
17114,
17137,
17157,
17216,
17265,
17266,
17333,
17334,
17358,
17426,
17490,
17558,
17626,
17661,
17662,
17684,
17707,
17711,
17770,
17774,
17775,
17797,
17820,
17868,
17917,
17918,
17972,
18034,
18061,
18123,
18167,
18190,
18230,
18288,
18328,
18329,
18349,
18398,
18399,
18465,
18471,
18472,
18488,
18537,
18538,
18592,
18593,
18601,
18650,
18651,
18703,
18762,
18773,
18799,
18800,
18864,
18875,
18910,
18911,
18975,
19000,
19062,
19109,
19110,
19130,
19192,
19203,
19263,
19274,
19275,
19339,
19388,
19389,
19449,
19495,
19557,
19622,
19633,
19698,
19763,
19777,
19842,
19853,
19905,
19973,
20009,
20010,
20018,
20067,
20068,
20080,
20146,
20205,
20206,
20218,
20286,
20314,
20315,
20347,
20396,
20397,
20464,
20526,
20593,
20658,
20671,
20672,
20712,
20755,
20756,
20819,
20872,
20936,
20945,
21013,
21080,
21094,
21095,
21119,
21168,
21169,
21233,
21258,
21283,
21284,
21304,
21353,
21354,
21422,
21469,
21470,
21492,
21515,
21559,
21608,
21609,
21671,
21735,
21756,
21801,
21825,
21888,
21953,
22014,
22015,
22037,
22060,
22076,
22123,
22124,
22174,
22175,
22215,
22264,
22265,
22326,
22344,
22406,
22425,
22477,
22503,
22557,
22558,
22580,
22603,
22623,
22672,
22673,
22733,
22791,
22792,
22800,
22849,
22850,
22866,
22928,
22995,
23006,
23007,
23059,
23117,
23185,
23249,
23280,
23281,
23335,
23336,
23403,
23469,
23527,
23593,
23631,
23632,
23654,
23677,
23705,
23754,
23755,
23822,
23885,
23949,
23970,
23971,
24019,
24068,
24069,
24136,
24204,
24232,
24233,
24296,
24362,
24427,
24494,
24521,
24522,
24558,
24607,
24608,
24672,
24736,
24804,
24856,
24921,
24940,
24941,
24985,
25034,
25035,
25100,
25168,
25179,
25180,
25235,
25236,
25301,
25332,
25333,
25341,
25390,
25391,
25403,
25471,
25484,
25485,
25513,
25579,
25644,
25711,
25776,
25844,
25880,
25881,
25889,
25938,
25939,
25943,
26007,
26011,
26076,
26080,
26081,
26165,
26217,
26257,
26306,
26364,
26376,
26429,
26495,
26515,
26578,
26598,
26658,
26716,
26774,
26831,
26871,
26923,
26963,
27008,
27064,
27119,
27120,
27128,
27177,
27178,
27194,
27261,
27325,
27356,
27357,
27369,
27437,
27452,
27453,
27473,
27527,
27528,
27594,
27601,
27602,
27630,
27679,
27680,
27749,
27797,
27845,
27883,
27884,
27906,
27929,
27945,
27994,
27995,
28019,
28020,
28044,
28093,
28094,
28154,
28190,
28246,
28247,
28259,
28308,
28309,
28368,
28390,
28413,
28417,
28466,
28488,
28511,
28515,
28544,
28548,
28549,
28571,
28594,
28602,
28651,
28652,
28674,
28697,
28705,
28730,
28731,
28753,
28776,
28792,
28838,
28887,
28937,
28938,
28962,
29011,
29012,
29074,
29085,
29117,
29118,
29126,
29175,
29176,
29184,
29250,
29251,
29263,
29319,
29377,
29378,
29400,
29423,
29431,
29491,
29492,
29512,
29574,
29585,
29645,
29656,
29657,
29677,
29735,
29785,
29834,
29835,
29893,
29897,
29898,
29910,
29975,
30015,
30016,
30020,
30072,
30076,
30099,
30107,
30162,
30217,
30221,
30269,
30273,
30320,
30324,
30325,
30349,
30413,
30428,
30496,
30521,
30571,
30572,
30580,
30650,
30696,
30700,
30701,
30733,
30799,
30812,
30813,
30878,
30924,
30925,
30978,
30979,
31001,
31024,
31040,
31095,
31156,
31179,
31180,
31200,
31249,
31250,
31301,
31363,
31364,
31372,
31421,
31422,
31430,
31484,
31485,
31501,
31565,
31630,
31659,
31660,
31672,
31735,
31747,
31748,
31760,
31826,
31855,
31856,
31876,
31941,
31979,
32010,
32062,
32063,
32071,
32120,
32121,
32125,
32193,
32215,
32238,
32242,
32297,
32319,
32342,
32346,
32375,
32383,
32447,
32497,
32519,
32542,
32546,
32547,
32559,
32627,
32642,
32643,
32651,
32700,
32701,
32713,
32779,
32839,
32840,
32864,
32932,
32996,
33062,
33127,
33144,
33145,
33169,
33218,
33219,
33285,
33348,
33361,
33362,
33402,
33451,
33452,
33510,
33523,
33579,
33633,
33692,
33753,
33766,
33767,
33789,
33812,
33856,
33905,
33906,
33970,
33978,
34038,
34055,
34099,
34143,
34204,
34243,
34244,
34252,
34301,
34302,
34310,
34362,
34363,
34375,
34443,
34475,
34476,
34488,
34537,
34538,
34606,
34610,
34648,
34652,
34653,
34675,
34698,
34722,
34771,
34772,
34803,
34870,
34915,
34916,
34938,
34961,
34969,
35018,
35019,
35041,
35064,
35088,
35152,
35218,
35283,
35303,
35334,
35335,
35351,
35419,
35471,
35491,
35492,
35514,
35537,
35561,
35592,
35659,
35675,
35741,
35794,
35795,
35815,
35864,
35865,
35933,
35979,
35980,
35988,
36037,
36038,
36058,
36125,
36188,
36248,
36293,
36294,
36314,
36376,
36440,
36505,
36522,
36523,
36539,
36588,
36589,
36613,
36614,
36646,
36695,
36696,
36758,
36823,
36887,
36954,
37003,
37004,
37020,
37069,
37070,
37113,
37114,
37136,
37159,
37179,
37228,
37229,
37296,
37317,
37318,
37326,
37375,
37376,
37384,
37445,
37446,
37454,
37508,
37509,
37531,
37554,
37570,
37624,
37686,
37731,
37732,
37754,
37777,
37785,
37834,
37835,
37847,
37908,
37928,
37929,
37951,
37974,
37986,
38045,
38104,
38105,
38113,
38162,
38163,
38183,
38250,
38303,
38370,
38409,
38410,
38418,
38477,
38478,
38490,
38556,
38601,
38602,
38634,
38683,
38684,
38749,
38811,
38879,
38943,
38951,
38952,
38976,
39025,
39026,
39092,
39117,
39171,
39172,
39192,
39241,
39242,
39299,
39351,
39352,
39368,
39417,
39418,
39475,
39476,
39528,
39577,
39578,
39646,
39668,
39735,
39746,
39791,
39831,
39876,
39916,
39958,
40009,
40010,
40022,
40080,
40146,
40147,
40155,
40204,
40205,
40233,
40296,
40361,
40395,
40396,
40457,
40479,
40480,
40512,
40575,
40597,
40666,
40727,
40790,
40835,
40890,
40891,
40899,
40948,
40949,
40971,
40994,
41006,
41074,
41138,
41139,
41167,
41198,
41253,
41317,
41382,
41388,
41435,
41436,
41458,
41481,
41497,
41546,
41547,
41594,
41595,
41617,
41640,
41648,
41697,
41698,
41746,
41813,
41839,
41840,
41906,
41939,
42001,
42024,
42025,
42085,
42148,
42197,
42198,
42220,
42243,
42255,
42321,
42332,
42333,
42341,
42390,
42391,
42399,
42443,
42444,
42454,
42514,
42515,
42570,
42619,
42620,
42676,
42677,
42708,
42756,
42808,
42848,
42888,
42928,
42929,
42954,
43003,
43004,
43071,
43094,
43095,
43120,
43169,
43170,
43227,
43286,
43287,
43332,
43381,
43382,
43445,
43508,
43532,
43582,
43625,
43693,
43694,
43704,
43753,
43754,
43764,
43822,
43861,
43876,
43943,
43989,
43990,
44012,
44035,
44045,
44094,
44095,
44117,
44140,
44150,
44176,
44177,
44199,
44222,
44242,
44298,
44360,
44405,
44406,
44431,
44480,
44481,
44546,
44604,
44605,
44630,
44679,
44680,
44744,
44790,
44791,
44811,
44860,
44861,
44885,
44886,
44891,
44940,
44945,
44946,
44981,
45043,
45101,
45169,
45182,
45183,
45243,
45244,
45254,
45312,
45375,
45390,
45454,
45522,
45584,
45589,
45590,
45605,
45672,
45703,
45704,
45709,
45758,
45763,
45764,
45784,
45844,
45892,
45938,
45939,
45961,
45984,
45999,
46042,
46097,
46098,
46103,
46162,
46172,
46235,
46245,
46250,
46251,
46256,
46305,
46310,
46311,
46376,
46443,
46490,
46527,
46562,
46596,
46638,
46639,
46685,
46686,
46753,
46785,
46815,
46816,
46826,
46882,
46883,
46888,
46937,
46942,
46943,
46958,
47016,
47060,
47061,
47076,
47138,
47190,
47191,
47206,
47272,
47318,
47319,
47324,
47373,
47378,
47379,
47424,
47485,
47552,
47559,
47589,
47622,
47684,
47752,
47802,
47803,
47823,
47887,
47951,
47971,
47972,
47994,
48017,
48027,
48075,
48076,
48106,
48172,
48224,
48255,
48310,
48327,
48328,
48353,
48384,
48448,
48460,
48513,
48514,
48519,
48568,
48573,
48574,
48604,
48666,
48717,
48777,
48841,
48847,
48892,
48902,
48969,
48991,
49061,
49126,
49141,
49209,
49220,
49288,
49355,
49366,
49426,
49485,
49511,
49570,
49625,
49670,
49734,
49739,
49740,
49745,
49794,
49816,
49839,
49864,
49865,
49932,
49941,
49973,
49974,
49979,
50028,
50050,
50073,
50078,
50079,
50104,
50166,
50202,
50241,
50291,
50292,
50314,
50337,
50347,
50413,
50414,
50419,
50468,
50473,
50474,
50494,
50562,
50628,
50652,
50653,
50658,
50725,
50730,
50783,
50803,
50870,
50903,
50957,
50958,
50963,
51012,
51027,
51028,
51078,
51079,
51089,
51138,
51139,
51179,
51229,
51278,
51343,
51393,
51457,
51476,
51533,
51534,
51594,
51656,
51687,
51747,
51758,
51818,
51829,
51891,
51912,
51948,
52016,
52027,
52028,
52098,
52165,
52227,
52294,
52337,
52396,
52462,
52469,
52528,
52560,
52599,
52651,
52719,
52748,
52749,
52759,
52808,
52809,
52824,
52883,
52894,
52895,
52910,
52977,
53025,
53026,
53041,
53090,
53091,
53157,
53162,
53210,
53215,
53216,
53226,
53275,
53276,
53326,
53392,
53458,
53493,
53547,
53568,
53599,
53645,
53709,
53745,
53746,
53766,
53824,
53873,
53940,
53941,
54066,
54115,
54116,
54179,
54221,
54284,
54307,
54371,
54434,
54496,
54497,
54546,
54547,
54591,
54637,
54683,
54729,
54773,
54817,
54863,
54907,
54955,
54997,
55045,
55087,
55088,
55098,
55147,
55148,
55173,
55215,
55259,
55324,
55336,
55337,
55387,
55449,
55467,
55499,
55500,
55573,
55574,
55624,
55690,
55706,
55707,
55732,
55754,
55821,
55885,
55924,
55925,
55975,
56024,
56025,
56092,
56156,
56166,
56231,
56294,
56303,
56338,
56339,
56349,
56398,
56399,
56421,
56444,
56484,
56551,
56552,
56602,
56643,
56687,
56723,
56761,
56762,
56817,
56878,
56905,
56937,
56966,
56990,
57016,
57017,
57080,
57148,
57209,
57210,
57220,
57269,
57270,
57285,
57344,
57367,
57368,
57408,
57464,
57507,
57528,
57529,
57589,
57618,
57649,
57650,
57660,
57711,
57712,
57722,
57771,
57772,
57807,
57851,
57875,
57923,
57972,
58019,
58068,
58069,
58094,
58141,
58142,
58195,
58229,
58230
],
"line_end_idx": [
17,
29,
51,
74,
78,
127,
128,
134,
199,
258,
259,
281,
304,
308,
376,
397,
401,
435,
488,
510,
533,
536,
537,
555,
604,
605,
669,
741,
786,
787,
809,
832,
904,
953,
954,
985,
1053,
1121,
1185,
1210,
1278,
1286,
1349,
1374,
1375,
1431,
1492,
1549,
1611,
1645,
1692,
1693,
1759,
1826,
1873,
1913,
1914,
1920,
1969,
1970,
1979,
2046,
2075,
2076,
2088,
2150,
2211,
2228,
2229,
2274,
2323,
2324,
2346,
2426,
2474,
2512,
2555,
2585,
2633,
2682,
2717,
2756,
2797,
2848,
2849,
2894,
2943,
2944,
3008,
3075,
3142,
3198,
3265,
3308,
3309,
3375,
3440,
3508,
3576,
3586,
3587,
3609,
3632,
3638,
3687,
3688,
3697,
3749,
3815,
3816,
3838,
3861,
3870,
3937,
3965,
3966,
4022,
4071,
4138,
4204,
4227,
4293,
4355,
4420,
4486,
4553,
4620,
4680,
4748,
4814,
4861,
4927,
4994,
4995,
5015,
5064,
5065,
5131,
5144,
5145,
5173,
5222,
5223,
5268,
5315,
5383,
5420,
5421,
5441,
5490,
5491,
5561,
5576,
5577,
5593,
5642,
5643,
5711,
5712,
5764,
5813,
5814,
5862,
5914,
5968,
5969,
6031,
6057,
6109,
6110,
6159,
6160,
6215,
6299,
6300,
6323,
6344,
6375,
6431,
6475,
6534,
6582,
6641,
6689,
6764,
6790,
6791,
6828,
6891,
6892,
6950,
6967,
6968,
7002,
7003,
7011,
7060,
7061,
7065,
7117,
7121,
7176,
7184,
7235,
7293,
7313,
7369,
7410,
7466,
7493,
7494,
7542,
7591,
7592,
7659,
7690,
7749,
7809,
7869,
7880,
7881,
7942,
7978,
7979,
8003,
8052,
8053,
8124,
8188,
8217,
8218,
8240,
8263,
8283,
8343,
8344,
8410,
8427,
8428,
8472,
8532,
8533,
8598,
8618,
8675,
8741,
8815,
8865,
8933,
8945,
8946,
8954,
9003,
9004,
9016,
9059,
9123,
9151,
9155,
9156,
9172,
9221,
9222,
9281,
9282,
9310,
9359,
9360,
9403,
9448,
9516,
9551,
9552,
9560,
9609,
9610,
9622,
9690,
9705,
9706,
9722,
9786,
9787,
9851,
9852,
9876,
9931,
9932,
9994,
10056,
10116,
10117,
10189,
10238,
10239,
10297,
10358,
10426,
10494,
10561,
10572,
10628,
10673,
10732,
10733,
10786,
10831,
10832,
10880,
10916,
10917,
10933,
10982,
10983,
11040,
11041,
11077,
11120,
11121,
11188,
11256,
11264,
11313,
11381,
11404,
11405,
11427,
11450,
11470,
11519,
11520,
11588,
11658,
11659,
11681,
11704,
11740,
11789,
11790,
11845,
11899,
11923,
11966,
12011,
12060,
12061,
12077,
12126,
12127,
12195,
12196,
12218,
12241,
12277,
12326,
12327,
12392,
12408,
12409,
12473,
12532,
12552,
12553,
12561,
12610,
12611,
12639,
12705,
12729,
12789,
12843,
12866,
12915,
12916,
12924,
12986,
12987,
12999,
13052,
13088,
13089,
13111,
13134,
13142,
13195,
13196,
13212,
13278,
13338,
13398,
13399,
13411,
13476,
13530,
13531,
13551,
13617,
13649,
13683,
13750,
13751,
13773,
13796,
13824,
13873,
13874,
13938,
14004,
14011,
14063,
14064,
14086,
14109,
14117,
14166,
14167,
14171,
14195,
14217,
14240,
14244,
14245,
14269,
14318,
14319,
14381,
14441,
14471,
14472,
14494,
14517,
14549,
14598,
14599,
14665,
14721,
14784,
14844,
14855,
14856,
14896,
14945,
14946,
15000,
15067,
15134,
15195,
15262,
15324,
15356,
15357,
15379,
15402,
15426,
15475,
15476,
15521,
15570,
15620,
15621,
15643,
15666,
15690,
15739,
15740,
15807,
15858,
15912,
15913,
15921,
15970,
15971,
15993,
16016,
16020,
16062,
16066,
16067,
16075,
16124,
16125,
16157,
16219,
16267,
16331,
16357,
16416,
16478,
16515,
16516,
16524,
16592,
16645,
16649,
16650,
16672,
16695,
16699,
16760,
16764,
16765,
16787,
16810,
16814,
16871,
16893,
16916,
16920,
16921,
16943,
16966,
16970,
17029,
17033,
17034,
17042,
17091,
17092,
17114,
17137,
17157,
17216,
17265,
17266,
17333,
17334,
17358,
17426,
17490,
17558,
17626,
17661,
17662,
17684,
17707,
17711,
17770,
17774,
17775,
17797,
17820,
17868,
17917,
17918,
17972,
18034,
18061,
18123,
18167,
18190,
18230,
18288,
18328,
18329,
18349,
18398,
18399,
18465,
18471,
18472,
18488,
18537,
18538,
18592,
18593,
18601,
18650,
18651,
18703,
18762,
18773,
18799,
18800,
18864,
18875,
18910,
18911,
18975,
19000,
19062,
19109,
19110,
19130,
19192,
19203,
19263,
19274,
19275,
19339,
19388,
19389,
19449,
19495,
19557,
19622,
19633,
19698,
19763,
19777,
19842,
19853,
19905,
19973,
20009,
20010,
20018,
20067,
20068,
20080,
20146,
20205,
20206,
20218,
20286,
20314,
20315,
20347,
20396,
20397,
20464,
20526,
20593,
20658,
20671,
20672,
20712,
20755,
20756,
20819,
20872,
20936,
20945,
21013,
21080,
21094,
21095,
21119,
21168,
21169,
21233,
21258,
21283,
21284,
21304,
21353,
21354,
21422,
21469,
21470,
21492,
21515,
21559,
21608,
21609,
21671,
21735,
21756,
21801,
21825,
21888,
21953,
22014,
22015,
22037,
22060,
22076,
22123,
22124,
22174,
22175,
22215,
22264,
22265,
22326,
22344,
22406,
22425,
22477,
22503,
22557,
22558,
22580,
22603,
22623,
22672,
22673,
22733,
22791,
22792,
22800,
22849,
22850,
22866,
22928,
22995,
23006,
23007,
23059,
23117,
23185,
23249,
23280,
23281,
23335,
23336,
23403,
23469,
23527,
23593,
23631,
23632,
23654,
23677,
23705,
23754,
23755,
23822,
23885,
23949,
23970,
23971,
24019,
24068,
24069,
24136,
24204,
24232,
24233,
24296,
24362,
24427,
24494,
24521,
24522,
24558,
24607,
24608,
24672,
24736,
24804,
24856,
24921,
24940,
24941,
24985,
25034,
25035,
25100,
25168,
25179,
25180,
25235,
25236,
25301,
25332,
25333,
25341,
25390,
25391,
25403,
25471,
25484,
25485,
25513,
25579,
25644,
25711,
25776,
25844,
25880,
25881,
25889,
25938,
25939,
25943,
26007,
26011,
26076,
26080,
26081,
26165,
26217,
26257,
26306,
26364,
26376,
26429,
26495,
26515,
26578,
26598,
26658,
26716,
26774,
26831,
26871,
26923,
26963,
27008,
27064,
27119,
27120,
27128,
27177,
27178,
27194,
27261,
27325,
27356,
27357,
27369,
27437,
27452,
27453,
27473,
27527,
27528,
27594,
27601,
27602,
27630,
27679,
27680,
27749,
27797,
27845,
27883,
27884,
27906,
27929,
27945,
27994,
27995,
28019,
28020,
28044,
28093,
28094,
28154,
28190,
28246,
28247,
28259,
28308,
28309,
28368,
28390,
28413,
28417,
28466,
28488,
28511,
28515,
28544,
28548,
28549,
28571,
28594,
28602,
28651,
28652,
28674,
28697,
28705,
28730,
28731,
28753,
28776,
28792,
28838,
28887,
28937,
28938,
28962,
29011,
29012,
29074,
29085,
29117,
29118,
29126,
29175,
29176,
29184,
29250,
29251,
29263,
29319,
29377,
29378,
29400,
29423,
29431,
29491,
29492,
29512,
29574,
29585,
29645,
29656,
29657,
29677,
29735,
29785,
29834,
29835,
29893,
29897,
29898,
29910,
29975,
30015,
30016,
30020,
30072,
30076,
30099,
30107,
30162,
30217,
30221,
30269,
30273,
30320,
30324,
30325,
30349,
30413,
30428,
30496,
30521,
30571,
30572,
30580,
30650,
30696,
30700,
30701,
30733,
30799,
30812,
30813,
30878,
30924,
30925,
30978,
30979,
31001,
31024,
31040,
31095,
31156,
31179,
31180,
31200,
31249,
31250,
31301,
31363,
31364,
31372,
31421,
31422,
31430,
31484,
31485,
31501,
31565,
31630,
31659,
31660,
31672,
31735,
31747,
31748,
31760,
31826,
31855,
31856,
31876,
31941,
31979,
32010,
32062,
32063,
32071,
32120,
32121,
32125,
32193,
32215,
32238,
32242,
32297,
32319,
32342,
32346,
32375,
32383,
32447,
32497,
32519,
32542,
32546,
32547,
32559,
32627,
32642,
32643,
32651,
32700,
32701,
32713,
32779,
32839,
32840,
32864,
32932,
32996,
33062,
33127,
33144,
33145,
33169,
33218,
33219,
33285,
33348,
33361,
33362,
33402,
33451,
33452,
33510,
33523,
33579,
33633,
33692,
33753,
33766,
33767,
33789,
33812,
33856,
33905,
33906,
33970,
33978,
34038,
34055,
34099,
34143,
34204,
34243,
34244,
34252,
34301,
34302,
34310,
34362,
34363,
34375,
34443,
34475,
34476,
34488,
34537,
34538,
34606,
34610,
34648,
34652,
34653,
34675,
34698,
34722,
34771,
34772,
34803,
34870,
34915,
34916,
34938,
34961,
34969,
35018,
35019,
35041,
35064,
35088,
35152,
35218,
35283,
35303,
35334,
35335,
35351,
35419,
35471,
35491,
35492,
35514,
35537,
35561,
35592,
35659,
35675,
35741,
35794,
35795,
35815,
35864,
35865,
35933,
35979,
35980,
35988,
36037,
36038,
36058,
36125,
36188,
36248,
36293,
36294,
36314,
36376,
36440,
36505,
36522,
36523,
36539,
36588,
36589,
36613,
36614,
36646,
36695,
36696,
36758,
36823,
36887,
36954,
37003,
37004,
37020,
37069,
37070,
37113,
37114,
37136,
37159,
37179,
37228,
37229,
37296,
37317,
37318,
37326,
37375,
37376,
37384,
37445,
37446,
37454,
37508,
37509,
37531,
37554,
37570,
37624,
37686,
37731,
37732,
37754,
37777,
37785,
37834,
37835,
37847,
37908,
37928,
37929,
37951,
37974,
37986,
38045,
38104,
38105,
38113,
38162,
38163,
38183,
38250,
38303,
38370,
38409,
38410,
38418,
38477,
38478,
38490,
38556,
38601,
38602,
38634,
38683,
38684,
38749,
38811,
38879,
38943,
38951,
38952,
38976,
39025,
39026,
39092,
39117,
39171,
39172,
39192,
39241,
39242,
39299,
39351,
39352,
39368,
39417,
39418,
39475,
39476,
39528,
39577,
39578,
39646,
39668,
39735,
39746,
39791,
39831,
39876,
39916,
39958,
40009,
40010,
40022,
40080,
40146,
40147,
40155,
40204,
40205,
40233,
40296,
40361,
40395,
40396,
40457,
40479,
40480,
40512,
40575,
40597,
40666,
40727,
40790,
40835,
40890,
40891,
40899,
40948,
40949,
40971,
40994,
41006,
41074,
41138,
41139,
41167,
41198,
41253,
41317,
41382,
41388,
41435,
41436,
41458,
41481,
41497,
41546,
41547,
41594,
41595,
41617,
41640,
41648,
41697,
41698,
41746,
41813,
41839,
41840,
41906,
41939,
42001,
42024,
42025,
42085,
42148,
42197,
42198,
42220,
42243,
42255,
42321,
42332,
42333,
42341,
42390,
42391,
42399,
42443,
42444,
42454,
42514,
42515,
42570,
42619,
42620,
42676,
42677,
42708,
42756,
42808,
42848,
42888,
42928,
42929,
42954,
43003,
43004,
43071,
43094,
43095,
43120,
43169,
43170,
43227,
43286,
43287,
43332,
43381,
43382,
43445,
43508,
43532,
43582,
43625,
43693,
43694,
43704,
43753,
43754,
43764,
43822,
43861,
43876,
43943,
43989,
43990,
44012,
44035,
44045,
44094,
44095,
44117,
44140,
44150,
44176,
44177,
44199,
44222,
44242,
44298,
44360,
44405,
44406,
44431,
44480,
44481,
44546,
44604,
44605,
44630,
44679,
44680,
44744,
44790,
44791,
44811,
44860,
44861,
44885,
44886,
44891,
44940,
44945,
44946,
44981,
45043,
45101,
45169,
45182,
45183,
45243,
45244,
45254,
45312,
45375,
45390,
45454,
45522,
45584,
45589,
45590,
45605,
45672,
45703,
45704,
45709,
45758,
45763,
45764,
45784,
45844,
45892,
45938,
45939,
45961,
45984,
45999,
46042,
46097,
46098,
46103,
46162,
46172,
46235,
46245,
46250,
46251,
46256,
46305,
46310,
46311,
46376,
46443,
46490,
46527,
46562,
46596,
46638,
46639,
46685,
46686,
46753,
46785,
46815,
46816,
46826,
46882,
46883,
46888,
46937,
46942,
46943,
46958,
47016,
47060,
47061,
47076,
47138,
47190,
47191,
47206,
47272,
47318,
47319,
47324,
47373,
47378,
47379,
47424,
47485,
47552,
47559,
47589,
47622,
47684,
47752,
47802,
47803,
47823,
47887,
47951,
47971,
47972,
47994,
48017,
48027,
48075,
48076,
48106,
48172,
48224,
48255,
48310,
48327,
48328,
48353,
48384,
48448,
48460,
48513,
48514,
48519,
48568,
48573,
48574,
48604,
48666,
48717,
48777,
48841,
48847,
48892,
48902,
48969,
48991,
49061,
49126,
49141,
49209,
49220,
49288,
49355,
49366,
49426,
49485,
49511,
49570,
49625,
49670,
49734,
49739,
49740,
49745,
49794,
49816,
49839,
49864,
49865,
49932,
49941,
49973,
49974,
49979,
50028,
50050,
50073,
50078,
50079,
50104,
50166,
50202,
50241,
50291,
50292,
50314,
50337,
50347,
50413,
50414,
50419,
50468,
50473,
50474,
50494,
50562,
50628,
50652,
50653,
50658,
50725,
50730,
50783,
50803,
50870,
50903,
50957,
50958,
50963,
51012,
51027,
51028,
51078,
51079,
51089,
51138,
51139,
51179,
51229,
51278,
51343,
51393,
51457,
51476,
51533,
51534,
51594,
51656,
51687,
51747,
51758,
51818,
51829,
51891,
51912,
51948,
52016,
52027,
52028,
52098,
52165,
52227,
52294,
52337,
52396,
52462,
52469,
52528,
52560,
52599,
52651,
52719,
52748,
52749,
52759,
52808,
52809,
52824,
52883,
52894,
52895,
52910,
52977,
53025,
53026,
53041,
53090,
53091,
53157,
53162,
53210,
53215,
53216,
53226,
53275,
53276,
53326,
53392,
53458,
53493,
53547,
53568,
53599,
53645,
53709,
53745,
53746,
53766,
53824,
53873,
53940,
53941,
54066,
54115,
54116,
54179,
54221,
54284,
54307,
54371,
54434,
54496,
54497,
54546,
54547,
54591,
54637,
54683,
54729,
54773,
54817,
54863,
54907,
54955,
54997,
55045,
55087,
55088,
55098,
55147,
55148,
55173,
55215,
55259,
55324,
55336,
55337,
55387,
55449,
55467,
55499,
55500,
55573,
55574,
55624,
55690,
55706,
55707,
55732,
55754,
55821,
55885,
55924,
55925,
55975,
56024,
56025,
56092,
56156,
56166,
56231,
56294,
56303,
56338,
56339,
56349,
56398,
56399,
56421,
56444,
56484,
56551,
56552,
56602,
56643,
56687,
56723,
56761,
56762,
56817,
56878,
56905,
56937,
56966,
56990,
57016,
57017,
57080,
57148,
57209,
57210,
57220,
57269,
57270,
57285,
57344,
57367,
57368,
57408,
57464,
57507,
57528,
57529,
57589,
57618,
57649,
57650,
57660,
57711,
57712,
57722,
57771,
57772,
57807,
57851,
57875,
57923,
57972,
58019,
58068,
58069,
58094,
58141,
58142,
58195,
58229,
58230,
58239
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 58239,
"ccnet_original_nlines": 1811,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.11749404668807983,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.014045779593288898,
"rps_doc_frac_lines_end_with_ellipsis": 0.0033112599048763514,
"rps_doc_frac_no_alph_words": 0.49256837368011475,
"rps_doc_frac_unique_words": 0.4479798674583435,
"rps_doc_mean_word_length": 6.448276042938232,
"rps_doc_num_sentences": 1482,
"rps_doc_symbol_to_word_ratio": 0.0012633800506591797,
"rps_doc_unigram_entropy": 6.9755377769470215,
"rps_doc_word_count": 6757,
"rps_doc_frac_chars_dupe_10grams": 0.007619750220328569,
"rps_doc_frac_chars_dupe_5grams": 0.11018797010183334,
"rps_doc_frac_chars_dupe_6grams": 0.09476487338542938,
"rps_doc_frac_chars_dupe_7grams": 0.04220696911215782,
"rps_doc_frac_chars_dupe_8grams": 0.031236369162797928,
"rps_doc_frac_chars_dupe_9grams": 0.026462560519576073,
"rps_doc_frac_chars_top_2gram": 0.05095132067799568,
"rps_doc_frac_chars_top_3gram": 0.08186638355255127,
"rps_doc_frac_chars_top_4gram": 0.03415115922689438,
"rps_doc_books_importance": -6319.0302734375,
"rps_doc_books_importance_length_correction": -6319.0302734375,
"rps_doc_openwebtext_importance": -3090.353271484375,
"rps_doc_openwebtext_importance_length_correction": -3090.353271484375,
"rps_doc_wikipedia_importance": -2188.569091796875,
"rps_doc_wikipedia_importance_length_correction": -2188.569091796875
},
"fasttext": {
"dclm": 0.4144231677055359,
"english": 0.5283982157707214,
"fineweb_edu_approx": 1.2991626262664795,
"eai_general_math": 0.08400958776473999,
"eai_open_web_math": 0.33810412883758545,
"eai_web_code": 0.581360936164856
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.82",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "003.54",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "System theory"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "4",
"label": "Code/Software"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "6",
"label": "Content Listing"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "4",
"label": "Graduate/Expert Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
4,207,175,559,519,915,500
|
Want to protect your cyber security and still get fast solutions? Ask a secure question today.Go Premium
x
• Status: Solved
• Priority: Medium
• Security: Public
• Views: 496
• Last Modified:
Unterminated string constant
Hi everyone hope you can help.
Guys i have another problem with a variable.
===================================
The following works:
===================================
function wz_tooltip_image ($image, $displaynamelink, $title) {
$stuffimage = "<a href=\"#\" $style onmouseover=\"$width; Tip('<img src=\'$image\'>',$wz_tooltip_config_text)\" onmouseout=\"UnTip()\">$displaynamelink</a>";
echo $stuffimage;
}
Calling it by:
<?php wz_tooltip_image("cat.jpg","Go there", $title); ?>
===================================
The following I cant get working:
===================================
function wz_tooltip_image ($image, $displaynamelink, $title) {
$stuffimage = "<a href=\"#\" $style onmouseover=\"$width; Tip('<img src=\'$image\'>',$wz_tooltip_config_text)\" onmouseout=\"UnTip()\">$displaynamelink</a>";
echo $stuffimage;
}
Calling it by:
wz_tooltip_image($row->image_ent, $row->name_ent, $row->name_ent);
The problem im having is with the $image parameter above.
In the first example, I hard code an image name, which worked, but in this case, the
$row->image_ent,
is pointing to a blob field in a mysql table.
Im getting unterminated string constants on this and cannot work out why.
I wanted to see if the images were okay in the database, separate from the above code, and I can display them fine, so there is something wrong with the way im escaping in the second example.
Any help guys greatly appreciated.
0
Simon336697
Asked:
Simon336697
• 18
• 7
• 5
• +1
3 Solutions
Roger BaklundCommented:
$image is supposed to contain an URL as a string. Why would you put a blob into it?
0
Guy Hengel [angelIII / a3]Billing EngineerCommented:
should that not be:
function wz_tooltip_image ($image, $displaynamelink, $title) {
$stuffimage = "<a href=\"#\" $style onmouseover=\"$width; Tip('<img src=\\'$image\\'>',$wz_tooltip_config_text)\" onmouseout=\"UnTip()\">$displaynamelink</a>";
echo $stuffimage;
}
Open in new window
0
Roger BaklundCommented:
Tip('<img src=\'$image\'>'
should be
('<img src=\"$image\" alt=\"\" />'
Allways double quotes for html attributes, allways use an alt attribute for image elements, and the ' />' ending is to make it xhtml compliant while at the same time beeing backward compatible with html.
0
Independent Software Vendors: We Want Your Opinion
We value your feedback.
Take our survey and automatically be enter to win anyone of the following:
Yeti Cooler, Amazon eGift Card, and Movie eGift Card!
Roger BaklundCommented:
You must of course keep "Tip":
Tip('<img src=\"$image\" alt=\"\" />'
0
Simon336697Author Commented:
Hi cxr,
Mate thank you for responding.
Im trying to display the images cxr.
What am i doing wrong bud?
What the function does is when im just hard coding the image name, i have a link, that when I hover over it, it displays that image.
With the other one im having issues with, im trying to do the same thing, except this time, all links are rows to records in a mysql table.
function wz_tooltip_image ($image, $displaynamelink, $title) {
Im going through a
while ($row = mysql_fetch_object($rs)) {
wz_tooltip_image($row->image_ent, $row->name_ent, $row->name_ent);
}
to do this..
0
hieloCommented:
>>is pointing to a blob field in a mysql table.
That's the problem. You can't point to the actual image binary data. Here's an experiment for you. Save some image (any image) to your desktop and then open it with notepad. What do you see?
Now when you code an HTML image tag you do so like this:
<img src="theImage.gif"...>
You do NOT provide the "raw image" in the src attribute. You provide the url to the image. The browser then submits another request to get the actual "raw image". So, your problem is that you are actually providing the "raw image". Instead what you need is provide a url to that image. In this case, create a php page (imageFetcher.php) that will retrieve the desired image if you provide the corresponding id. So in you case instead of:
wz_tooltip_image($row->image_ent, $row->name_ent, $row->name_ent);
use:
wz_tooltip_image("http://www.yoursite.com/imageFetcher.php?id=" . $row->image_id, $row->name_ent, $row->name_ent);
you would of course need to code imageFetcher.php:
<?php
//send appropriate header:
header("Content-type: image/jpg");
//connect to db here
//then query db for desired image:
$result = mysql_query("SELECT image_ent FROM images where id=" . $_GET['id']);
$image=mysql_fetch_assoc($result);
echo $image['image_ent'];
?>
Open in new window
0
Simon336697Author Commented:
The wz_tooltip_image is a function that displays tooltips, and you can put images inside the tooltip, so im trying to get the blob image into it.
I can successfully get other text fields into the tooltip, but having issues with the blob image.
When i hard code the image, i can see that in the tooltip, so i dont know what is wrong when im using
$row->image_ent,
0
hieloCommented:
>>so im trying to get the blob image into it.
It's not going to work. Read my previous comment. Use the imageFetcher.php I provided. Make sure you connect to the db first.
NOTE: for it to work, on the code you posted you need to retrieve a unique per image
0
Simon336697Author Commented:
Thanks so much hielo....I will give it a try now mate youre the best :>)
0
Simon336697Author Commented:
Hielo bud,
Ive changed the function to be like this...
=========================================================== index2.php
function wz_tooltip_image ($image) {
$wz_tooltip_config_image = "
STICKY, true,
FIX, [740,235],
WIDTH, 870,
HEIGHT, 565,
BGCOLOR, 'black',
TITLE, 'df',
TITLEFONTCOLOR, '#FFC',
TITLEBGCOLOR, '#664',
EXCLUSIVE, false,
CLICKSTICKY, true,
CLICKCLOSE, false,
CLOSEBTN, true
";
$styleimage = "style=\"font-family:arial; font-size:xx-small; padding:0; margin:0; border:none;\"";
$stuffimage = "<a href=\"#\" $styleimage onmouseover=\"Tip($image,$wz_tooltip_config_image)\" onmouseout=\"UnTip()\">displaynamelink</a>";
echo $stuffimage;
}
==============================================
and in the while loop, calling it like:
wz_tooltip_image("http://localhost/dropdowndbpilot/pagination/imagefetcher.php?id_ent=" . $row->id_ent);
In the imagefetcher.php file, i have the following...
<?php
//send appropriate header:
header("Content-type: image/jpg");
//connect to db here
$host = "localhost";
$user = "root";
$pass = "password";
$data = "pagination";
$conn = mysql_connect($host, $user, $pass) or die (mysql_error());
mysql_select_db ($data, $conn) or die (mysql_error());
//then query db for desired image:
$getme = $_GET['id_ent'];
$result = mysql_query("SELECT image_ent FROM entries_ent where id_ent='$getme'");
$image=mysql_fetch_assoc($result);
echo $image['image_ent'];
?>
====================
If i open up image_fetcher.php on its own, and just change the $getme to a valid id, I get the image displayed.
But when I run index2.php, Im getting
Error: Expected ')'
For every row.
0
Simon336697Author Commented:
hielo mate,
where you have...
wz_tooltip_image("http://www.yoursite.com/imageFetcher.php?id=" . $row->image_id, $row->name_ent, $row->name_ent);
the wz_tooltip_image wants each parameter in single quotes.
Im only using the ?id=" . $row->image_id bit and not $row->name_ent, $row->name_ent
but how would i encapsulate
wz_tooltip_image("http://www.yoursite.com/imageFetcher.php?id=" . $row->image_id)
the above so it would be:
wz_tooltip_image(' above url ');
0
hieloCommented:
try:
function wz_tooltip_image ($image) {
$wz_tooltip_config_image = "STICKY, true, FIX, [740,235], WIDTH, 870, HEIGHT, 565, BGCOLOR, 'black', TITLE, 'df', TITLEFONTCOLOR, '#FFC', TITLEBGCOLOR, '#664', EXCLUSIVE, false, CLICKSTICKY, true, CLICKCLOSE, false, CLOSEBTN, true";
$styleimage = "font-family:arial; font-size:xx-small; padding:0; margin:0; border:none;";
printf('<a href="#" style="%s" onmouseover="Tip(\'%s\',%s)" onmouseout="UnTip()">displaynamelink</a>'
,$styleimage
,$image
,$wz_tooltip_config_image
);
}
Open in new window
0
Simon336697Author Commented:
Thanks hielo mate. will do right now :>) you are so helpful
0
Simon336697Author Commented:
Hielo, I tested yours mate and here are the results...
=========================================== index2.php
Your function...
wz_tooltip_image("http://localhost/dropdowndbpilot/pagination/imagefetcher.php?id_ent=" . $row->id_ent);
===================================== in image_fetcher.php
//send appropriate header:
header("Content-type: image/jpg");
//connect to db here
$host = "localhost";
$user = "root";
$pass = "password";
$data = "pagination";
$conn = mysql_connect($host, $user, $pass) or die (mysql_error());
mysql_select_db ($data, $conn) or die (mysql_error());
//then query db for desired image:
$getme = $_GET['id_ent'];
$result = mysql_query("SELECT image_ent FROM entries_ent where id_ent='$getme'");
$image=mysql_fetch_assoc($result);
echo $image['image_ent'];
?>
=================================================
Hielo, for each record displayed, it is just printing out:
http://localhost/dropdowndbpilot/pagination/imagefetcher.php?id_ent=5387
in the tooltip and not the image.
It does not error either if i totally change the name of the URL above.
The ids are being returned right, but the url looks like it is being ignored.
If I hard code an image where the
http://localhost/dropdowndbpilot/pagination/imagefetcher.php?id_ent=5387
is, and do this outside a while loop, it works.
0
Simon336697Author Commented:
Hielo,
Ill upload an example with all files that work with a hard coded image.
0
Roger BaklundCommented:
You are not outputting an html img now, so this behaviour is correct.
$image now contains "http://localhost/dropdowndbpilot/pagination/imagefetcher.php?id_ent=" . $row->id_ent
It should contain '<img src="http://localhost/dropdowndbpilot/pagination/imagefetcher.php?id_ent='.$row->id_ent.'" alt="" />'
Because this will be used within a " quoted html attribute, there must be an \ before each ", and because PHP will 'eat' a single backslash, you must double them:
'<img src=\\"http://localhost/dropdowndbpilot/pagination/imagefetcher.php?id_ent='.$row->id_ent.'\\" alt=\\"\\" />'
So, try this call to wz_tooltip_image():
wz_tooltip_image('<img src=\\"http://localhost/dropdowndbpilot/pagination/imagefetcher.php?id_ent='.$row->id_ent.'\\" alt=\\"\\" />');
Open in new window
0
Simon336697Author Commented:
Hielo mate.
Here is a working example of what im trying to do mate.
In the code snippet, is the php file for it.
=========================================== hielo.php
<?php
function wz_tooltip_image ($image, $displaynamelink, $title) {
$wz_tooltip_config_text = "
STICKY, true,
FIX, [240,210],
WIDTH, 300,
HEIGHT, 100,
BGCOLOR, '#ffff80',
TITLE, '$title',
TITLEFONTCOLOR, '#FFC',
TITLEBGCOLOR, '#664',
EXCLUSIVE, false,
CLICKSTICKY, true,
CLOSEBTN, true
";
$style = "style=\"font-size:xx-small;\"";
$stuff = "<a href=\"#\" $style onmouseover=\"$width; Tip('<img src=\'$image\'>',$wz_tooltip_config_text)\" onmouseout=\"UnTip()\">$displaynamelink</a>";
echo $stuff;
}
$title = "Hi Champion Hielo";
?>
<?php // wz_tooltip_text($text,"Go there", $title); ?><br>
<?php wz_tooltip_image("cat.jpg","Go there", $title); ?><br>
</body>
</html>
============================================================
Open in new window
cat.jpg
tip-centerwindow.txt
tip-followscroll.txt
wz-tooltip.txt
hielo.jpg
0
Simon336697Author Commented:
Thanks so much as well cxr.....pls see above.......im reading your post now...you guys are brilliant.
0
hieloCommented:
Simon, on the code I provided here (ID: 22763196) I was "fixing" what you supplied here (ID: 22762966). Upon closer inspection, that code you supplied is different from what you posted originally in the problem description. Why did you you remove the img tag from the Tip() argument?
0
hieloCommented:
function wz_tooltip_image ($image) {
$wz_tooltip_config_image = "STICKY, true, FIX, [740,235], WIDTH, 870, HEIGHT, 565, BGCOLOR, 'black', TITLE, 'df', TITLEFONTCOLOR, '#FFC', TITLEBGCOLOR, '#664', EXCLUSIVE, false, CLICKSTICKY, true, CLICKCLOSE, false, CLOSEBTN, true";
$styleimage = "font-family:arial; font-size:xx-small; padding:0; margin:0; border:none;";
printf('<a href="#" style="%s" onmouseover="Tip(\'<img src=\"%s\">\',%s)" onmouseout="UnTip()">displaynamelink</a>'
,$styleimage
,$image
,$wz_tooltip_config_image
);
}
Open in new window
0
Simon336697Author Commented:
Hi cx, with the following config, i get an unterminated string constant..
======================================= index2.php
function wz_tooltip_image ($image) {
$wz_tooltip_config_image = "
STICKY, true,
FIX, [740,235],
WIDTH, 870,
HEIGHT, 565,
BGCOLOR, 'black',
TITLE, 'df',
TITLEFONTCOLOR, '#FFC',
TITLEBGCOLOR, '#664',
EXCLUSIVE, false,
CLICKSTICKY, true,
CLICKCLOSE, false,
CLOSEBTN, true
";
$styleimage = "style=\"font-family:arial; font-size:xx-small; padding:0; margin:0; border:none;\"";
$stuffimage = "<a href=\"#\" $styleimage onmouseover=\"Tip('$image',$wz_tooltip_config_image)\" onmouseout=\"UnTip()\">displaynamelink</a>";
echo $stuffimage;
}
=======================================================
wz_tooltip_image('<img src=\\"http://localhost/dropdowndbpilot/pagination/imagefetcher.php?id_ent='.$row->id_ent.'\\" alt=\\"\\" />');
Open in new window
0
Simon336697Author Commented:
Sorry hielo....im testing so much stuff here (and i know you great person and cxr are as well).
Bear with me im all over the place..
0
Simon336697Author Commented:
Hielo mate...
im going to try again with your post from 22763436.
Mate im sorry but how do i call the function?
0
Simon336697Author Commented:
If I call it like:
wz_tooltip_image(http://localhost/dropdowndbpilot/pagination/imagefetcher.php?id_ent='.$row->id_ent);
I get unexpected : (after the http)
I must be getting tired sorry guys u are so patient
0
Simon336697Author Commented:
With this..
wz_tooltip_image('http://localhost/dropdowndbpilot/pagination/imagefetcher.php?id_ent='.$row->id_ent');
I get:
Warning: Unexpected character in input: ''' (ASCII=39) state=1 in C:\wamp\www\dropdowndbpilot\pagination\index2.php on line 496
0
Roger BaklundCommented:
Yes, sorry Simon, my suggestion was wrong. I have done some tests, and I can't find a way to do this correctly. With 'this', I mean to output correct html with attribute values enclosed in double quotes, from within a html attribute.
One possible workaround is to drop the quotes, it will work in most browsers, but it is not standards compliant. Same goes for using single quotes. Will work in most browsers, but it is not standards compliant.
I think the best way is to use a wrapper function. Define this in head, within <script> tags:
function MyTip(img,conf) {
Tip('<img src="'+img+'" alt="" />',conf);
}
...and call MyTip() in place of Tip() in your existing code. This way we move the double quotes in the img element attributes out of the onclick attribute, and it is no longer a problem.
0
Simon336697Author Commented:
Hi cxr, thanks for that..
Im embarrassed.....what version of my code would i use this with....sorry...im overtired.
0
Roger BaklundCommented:
To show the image in the tooltip, you need to include a html img element, i.e. a string like this:
<img src="image-URL-here" alt="" />
You had this in earlier versions of the wz_tooltip_image() PHP function.
The Tip() function is a javascript function, and you call it within the onclick attribute of the <a href="#" within the wz_tooltip_image() PHP function. Since you are allready within double quotes in the onclick attribute, you can not use double quotes in the Tip() function call:
onclick="Tip('double quotes not allowed here');"
In one of the above posts (ID: 22763257) you had the code working, it did not output any images because there was no html img element. If you changed Tip() to MyTip() in that version, and included the MyTip() function within <script> tags in the head part of the document, it should show the images.
0
Roger BaklundCommented:
Sorry, it's not onclick, it's onmouseover. I'm getting tired too. :)
0
Simon336697Author Commented:
Hi cxr,
Thank you so much for your great help mate.
And hielo..you guys are awesome.
Ill post another one on this and revisit it...i still cant get it working, but so much want to.
Mate thanks again...
Im going to try again in a few hours and post back my findings :>)
0
Simon336697Author Commented:
Guys, firstly...A HUGE HUGE THANK YOU to you..
Hielo,
Angellll
Cxr
You are so very patient with me.
Because this is so long, Im going to give you the points now and post another more cleaner up to date question on this.
I thank you so much.
0
Featured Post
VIDEO: THE CONCERTO CLOUD FOR HEALTHCARE
Modern healthcare requires a modern cloud. View this brief video to understand how the Concerto Cloud for Healthcare can help your organization.
• 18
• 7
• 5
• +1
Tackle projects and never again get stuck behind a technical roadblock.
Join Now
|
{
"url": "https://www.experts-exchange.com/questions/23831350/Unterminated-string-constant.html",
"source_domain": "www.experts-exchange.com",
"snapshot_id": "crawl=CC-MAIN-2018-05",
"warc_metadata": {
"Content-Length": "250177",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:2AVCUJM3G76UWHJRPQGACWPMAHY7KL5C",
"WARC-Concurrent-To": "<urn:uuid:361480a4-bee4-4207-88a8-463730288222>",
"WARC-Date": "2018-01-19T02:32:32Z",
"WARC-IP-Address": "104.20.168.10",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:VDKBPUYBZRL5NXVFWAVLHM3KITNBCIJX",
"WARC-Record-ID": "<urn:uuid:96acaf50-3525-4255-a672-1c80929a30db>",
"WARC-Target-URI": "https://www.experts-exchange.com/questions/23831350/Unterminated-string-constant.html",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:e97d28ef-0e58-4e78-a73a-92df689dbf16>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-181-179-14.ec2.internal\r\nsoftware: Nutch 1.6 (CC)\r\nisPartOf: CC-MAIN-2018-05\r\noperator: Common Crawl Admin\r\ndescription: Wide crawl of the web for January 2018\r\npublisher: Common Crawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
105,
106,
108,
127,
148,
169,
184,
203,
204,
233,
234,
265,
266,
311,
312,
348,
369,
405,
468,
626,
644,
646,
647,
662,
663,
720,
721,
757,
791,
827,
890,
1048,
1066,
1068,
1069,
1084,
1157,
1158,
1216,
1301,
1302,
1319,
1320,
1366,
1440,
1632,
1633,
1668,
1670,
1682,
1689,
1701,
1708,
1714,
1720,
1727,
1739,
1741,
1765,
1849,
1851,
1853,
1906,
1926,
1989,
2149,
2167,
2169,
2170,
2189,
2190,
2192,
2194,
2218,
2245,
2246,
2256,
2257,
2292,
2293,
2497,
2499,
2550,
2551,
2575,
2576,
2651,
2705,
2706,
2708,
2732,
2763,
2764,
2802,
2804,
2806,
2835,
2843,
2874,
2911,
2938,
2939,
3072,
3073,
3213,
3276,
3295,
3296,
3337,
3404,
3406,
3407,
3420,
3421,
3422,
3423,
3424,
3426,
3428,
3444,
3492,
3683,
3684,
3741,
3770,
4208,
4278,
4283,
4401,
4452,
4458,
4485,
4521,
4542,
4577,
4657,
4692,
4718,
4721,
4722,
4741,
4742,
4744,
4746,
4775,
4921,
5019,
5121,
5138,
5140,
5142,
5158,
5204,
5330,
5331,
5416,
5418,
5420,
5449,
5522,
5524,
5526,
5555,
5566,
5567,
5611,
5612,
5683,
5720,
5749,
5763,
5779,
5793,
5806,
5824,
5837,
5861,
5885,
5903,
5922,
5941,
5956,
5959,
6059,
6198,
6216,
6218,
6265,
6266,
6306,
6307,
6412,
6413,
6467,
6468,
6474,
6501,
6536,
6557,
6578,
6594,
6614,
6636,
6709,
6782,
6817,
6843,
6925,
6960,
6986,
6989,
6990,
6991,
7012,
7013,
7125,
7126,
7164,
7184,
7199,
7200,
7201,
7202,
7203,
7205,
7207,
7236,
7248,
7249,
7267,
7268,
7385,
7386,
7446,
7530,
7558,
7559,
7641,
7642,
7668,
7701,
7702,
7704,
7706,
7722,
7727,
7764,
7998,
8088,
8090,
8192,
8206,
8215,
8242,
8246,
8248,
8249,
8268,
8269,
8271,
8273,
8302,
8362,
8364,
8366,
8395,
8450,
8451,
8506,
8507,
8524,
8525,
8630,
8631,
8632,
8691,
8692,
8719,
8754,
8775,
8796,
8812,
8832,
8854,
8927,
9000,
9035,
9061,
9143,
9178,
9204,
9207,
9208,
9258,
9259,
9318,
9319,
9392,
9393,
9427,
9428,
9500,
9578,
9579,
9613,
9686,
9734,
9735,
9736,
9737,
9739,
9741,
9770,
9777,
9849,
9851,
9853,
9877,
9947,
9948,
10055,
10056,
10182,
10183,
10346,
10347,
10463,
10464,
10505,
10640,
10641,
10660,
10661,
10663,
10665,
10694,
10706,
10707,
10763,
10764,
10809,
10863,
10865,
10871,
10873,
10936,
10938,
10966,
10981,
10998,
11012,
11026,
11047,
11065,
11090,
11114,
11133,
11153,
11168,
11174,
11176,
11218,
11371,
11384,
11386,
11388,
11418,
11421,
11423,
11425,
11484,
11486,
11547,
11549,
11557,
11559,
11561,
11569,
11630,
11631,
11650,
11651,
11659,
11680,
11701,
11716,
11726,
11728,
11730,
11759,
11861,
11863,
11865,
11881,
12165,
12167,
12169,
12185,
12186,
12223,
12457,
12547,
12549,
12665,
12679,
12688,
12715,
12719,
12721,
12722,
12741,
12742,
12744,
12746,
12775,
12849,
12900,
12902,
12939,
12941,
12970,
12985,
13002,
13016,
13030,
13049,
13063,
13088,
13112,
13131,
13151,
13170,
13185,
13191,
13193,
13293,
13434,
13452,
13454,
13456,
13512,
13647,
13648,
13667,
13668,
13670,
13672,
13701,
13797,
13834,
13836,
13838,
13867,
13881,
13882,
13934,
13935,
13981,
13983,
13985,
14014,
14033,
14034,
14136,
14137,
14175,
14176,
14228,
14230,
14232,
14261,
14273,
14274,
14378,
14379,
14386,
14387,
14515,
14517,
14519,
14543,
14777,
14778,
14989,
14990,
15084,
15085,
15112,
15156,
15158,
15159,
15346,
15348,
15350,
15379,
15405,
15495,
15497,
15499,
15523,
15622,
15623,
15659,
15660,
15733,
15734,
16015,
16016,
16065,
16066,
16366,
16368,
16370,
16394,
16463,
16465,
16467,
16496,
16504,
16548,
16581,
16677,
16698,
16765,
16767,
16769,
16798,
16845,
16852,
16861,
16865,
16866,
16899,
17019,
17040,
17042,
17043,
17057,
17058,
17099,
17100,
17245,
17246,
17253,
17259,
17265,
17272,
17344
],
"line_end_idx": [
105,
106,
108,
127,
148,
169,
184,
203,
204,
233,
234,
265,
266,
311,
312,
348,
369,
405,
468,
626,
644,
646,
647,
662,
663,
720,
721,
757,
791,
827,
890,
1048,
1066,
1068,
1069,
1084,
1157,
1158,
1216,
1301,
1302,
1319,
1320,
1366,
1440,
1632,
1633,
1668,
1670,
1682,
1689,
1701,
1708,
1714,
1720,
1727,
1739,
1741,
1765,
1849,
1851,
1853,
1906,
1926,
1989,
2149,
2167,
2169,
2170,
2189,
2190,
2192,
2194,
2218,
2245,
2246,
2256,
2257,
2292,
2293,
2497,
2499,
2550,
2551,
2575,
2576,
2651,
2705,
2706,
2708,
2732,
2763,
2764,
2802,
2804,
2806,
2835,
2843,
2874,
2911,
2938,
2939,
3072,
3073,
3213,
3276,
3295,
3296,
3337,
3404,
3406,
3407,
3420,
3421,
3422,
3423,
3424,
3426,
3428,
3444,
3492,
3683,
3684,
3741,
3770,
4208,
4278,
4283,
4401,
4452,
4458,
4485,
4521,
4542,
4577,
4657,
4692,
4718,
4721,
4722,
4741,
4742,
4744,
4746,
4775,
4921,
5019,
5121,
5138,
5140,
5142,
5158,
5204,
5330,
5331,
5416,
5418,
5420,
5449,
5522,
5524,
5526,
5555,
5566,
5567,
5611,
5612,
5683,
5720,
5749,
5763,
5779,
5793,
5806,
5824,
5837,
5861,
5885,
5903,
5922,
5941,
5956,
5959,
6059,
6198,
6216,
6218,
6265,
6266,
6306,
6307,
6412,
6413,
6467,
6468,
6474,
6501,
6536,
6557,
6578,
6594,
6614,
6636,
6709,
6782,
6817,
6843,
6925,
6960,
6986,
6989,
6990,
6991,
7012,
7013,
7125,
7126,
7164,
7184,
7199,
7200,
7201,
7202,
7203,
7205,
7207,
7236,
7248,
7249,
7267,
7268,
7385,
7386,
7446,
7530,
7558,
7559,
7641,
7642,
7668,
7701,
7702,
7704,
7706,
7722,
7727,
7764,
7998,
8088,
8090,
8192,
8206,
8215,
8242,
8246,
8248,
8249,
8268,
8269,
8271,
8273,
8302,
8362,
8364,
8366,
8395,
8450,
8451,
8506,
8507,
8524,
8525,
8630,
8631,
8632,
8691,
8692,
8719,
8754,
8775,
8796,
8812,
8832,
8854,
8927,
9000,
9035,
9061,
9143,
9178,
9204,
9207,
9208,
9258,
9259,
9318,
9319,
9392,
9393,
9427,
9428,
9500,
9578,
9579,
9613,
9686,
9734,
9735,
9736,
9737,
9739,
9741,
9770,
9777,
9849,
9851,
9853,
9877,
9947,
9948,
10055,
10056,
10182,
10183,
10346,
10347,
10463,
10464,
10505,
10640,
10641,
10660,
10661,
10663,
10665,
10694,
10706,
10707,
10763,
10764,
10809,
10863,
10865,
10871,
10873,
10936,
10938,
10966,
10981,
10998,
11012,
11026,
11047,
11065,
11090,
11114,
11133,
11153,
11168,
11174,
11176,
11218,
11371,
11384,
11386,
11388,
11418,
11421,
11423,
11425,
11484,
11486,
11547,
11549,
11557,
11559,
11561,
11569,
11630,
11631,
11650,
11651,
11659,
11680,
11701,
11716,
11726,
11728,
11730,
11759,
11861,
11863,
11865,
11881,
12165,
12167,
12169,
12185,
12186,
12223,
12457,
12547,
12549,
12665,
12679,
12688,
12715,
12719,
12721,
12722,
12741,
12742,
12744,
12746,
12775,
12849,
12900,
12902,
12939,
12941,
12970,
12985,
13002,
13016,
13030,
13049,
13063,
13088,
13112,
13131,
13151,
13170,
13185,
13191,
13193,
13293,
13434,
13452,
13454,
13456,
13512,
13647,
13648,
13667,
13668,
13670,
13672,
13701,
13797,
13834,
13836,
13838,
13867,
13881,
13882,
13934,
13935,
13981,
13983,
13985,
14014,
14033,
14034,
14136,
14137,
14175,
14176,
14228,
14230,
14232,
14261,
14273,
14274,
14378,
14379,
14386,
14387,
14515,
14517,
14519,
14543,
14777,
14778,
14989,
14990,
15084,
15085,
15112,
15156,
15158,
15159,
15346,
15348,
15350,
15379,
15405,
15495,
15497,
15499,
15523,
15622,
15623,
15659,
15660,
15733,
15734,
16015,
16016,
16065,
16066,
16366,
16368,
16370,
16394,
16463,
16465,
16467,
16496,
16504,
16548,
16581,
16677,
16698,
16765,
16767,
16769,
16798,
16845,
16852,
16861,
16865,
16866,
16899,
17019,
17040,
17042,
17043,
17057,
17058,
17099,
17100,
17245,
17246,
17253,
17259,
17265,
17272,
17344,
17352
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 17352,
"ccnet_original_nlines": 548,
"rps_doc_curly_bracket": 0.0012102399487048388,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.24061989784240723,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.033170200884342194,
"rps_doc_frac_lines_end_with_ellipsis": 0.012750459834933281,
"rps_doc_frac_no_alph_words": 0.3605220317840576,
"rps_doc_frac_unique_words": 0.2750118374824524,
"rps_doc_mean_word_length": 5.7230916023254395,
"rps_doc_num_sentences": 196,
"rps_doc_symbol_to_word_ratio": 0.010875480249524117,
"rps_doc_unigram_entropy": 5.675691604614258,
"rps_doc_word_count": 2109,
"rps_doc_frac_chars_dupe_10grams": 0.26859983801841736,
"rps_doc_frac_chars_dupe_5grams": 0.32908037304878235,
"rps_doc_frac_chars_dupe_6grams": 0.29502901434898376,
"rps_doc_frac_chars_dupe_7grams": 0.2864125967025757,
"rps_doc_frac_chars_dupe_8grams": 0.2829328775405884,
"rps_doc_frac_chars_dupe_9grams": 0.26859983801841736,
"rps_doc_frac_chars_top_2gram": 0.02684340998530388,
"rps_doc_frac_chars_top_3gram": 0.040265120565891266,
"rps_doc_frac_chars_top_4gram": 0.008699250407516956,
"rps_doc_books_importance": -1849.422119140625,
"rps_doc_books_importance_length_correction": -1849.422119140625,
"rps_doc_openwebtext_importance": -800.1477661132812,
"rps_doc_openwebtext_importance_length_correction": -800.1477661132812,
"rps_doc_wikipedia_importance": -636.7786865234375,
"rps_doc_wikipedia_importance_length_correction": -636.7786865234375
},
"fasttext": {
"dclm": 0.2869751453399658,
"english": 0.6526312232017517,
"fineweb_edu_approx": 1.9376214742660522,
"eai_general_math": 0.15365809202194214,
"eai_open_web_math": 0.3046255111694336,
"eai_web_code": 0.03589421883225441
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.133",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "4",
"label": "Analyze"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "2",
"label": "Partially Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
1,424,802,274,296,374,000
|
aom-rav1e:1b5e9871f7a4fe7b89da047df046b0cfb4b3566d commits https://gitlab.xiph.org/xiph/aom-rav1e/-/commits/1b5e9871f7a4fe7b89da047df046b0cfb4b3566d 2014-07-11T10:30:25-07:00 https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/1b5e9871f7a4fe7b89da047df046b0cfb4b3566d Code refactoring: use defined inline functions 2014-07-11T10:30:25-07:00 Yunqing Wang yunqingwang@google.com Changed to use defined inline functions consistently through the code. Change-Id: I7644d24fa7a837378564a6e0790416d3725dd200 https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/8a7cc1f47bde271c5200550f1f7e7f6a55872b65 Merge "update vp9_thread.c" 2014-07-10T23:19:55-07:00 James Zern jzern@google.com https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/c00e9c4709c1ac3828ce13aae158011495e7de35 Merge changes Ie241772d,I3c72e226 2014-07-10T21:11:40-07:00 James Zern jzern@google.com * changes: tests: add API_REGISTER_STATE_CHECK call vp[89]_clear_system_state after longjmp https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/32655853266a7bc975f825a00df96d40f9e85658 Merge "Minor cleanup" 2014-07-10T16:39:48-07:00 Yaowu Xu yaowu@google.com https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/f3544f079b4fd62694216374432d91437f06c8a1 Merge "sh tests: Add support for running tested programs within another progr... 2014-07-10T16:16:06-07:00 Tom Finegan tomfinegan@google.com https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/7a22d8ba833a285745f34e7c8fea84a0a6eb5939 Merge "Add warning to temporal SVC test when temporal denoising is disabled." 2014-07-10T15:34:30-07:00 Tom Finegan tomfinegan@google.com https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/926a6f63cb362098cb5ee5332f0e8149ae452675 sh tests: Add support for running tested programs within another program. 2014-07-10T15:32:01-07:00 Tom Finegan tomfinegan@google.com Specifying the --prefix command line arg executes all test programs within the context of the prefix string, which is assigned to VPX_TEST_PREFIX. All test functions updated to include VPX_TEST_PREFIX in their eval command. Change-Id: I2e215cc8f216048edf3269db02a6b5660fe32318 https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/4eae56d6601365da03ba8a1138674941a9b7cf8a Add warning to temporal SVC test when temporal denoising is disabled. 2014-07-10T14:52:31-07:00 Tom Finegan tomfinegan@google.com Change-Id: Ib3792aa93514ccaf06c5d3f737f6e9243096f61c https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/29e1b1a4b082992d0e84ee721afaadcd4db5e626 tests: add API_REGISTER_STATE_CHECK 2014-07-10T12:40:31-07:00 James Zern jzern@google.com used to wrap API functions to ensure full environment consistency as opposed to the renamed ASM_REGISTER_STATE_CHECK which is used with assembly functions. currently checks the FPU tag word in x86/x86_64 gcc builds to ensure emms has been called. Change-Id: Ie241772dbf903d33d516a1add4c8c6783f2e1490 https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/61c3338516af9daeb65eaa47e7fae8428facae5f call vp[89]_clear_system_state after longjmp 2014-07-10T12:36:28-07:00 James Zern jzern@google.com restore the environment post encode/decode failure Change-Id: I3c72e2260a616432eaf1f9545d4fb4d8e45cc7b0 https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/8701ed0270dd8da44efff5e19f3b0b6d3cac5b8b update vp9_thread.c 2014-07-10T12:20:54-07:00 James Zern jzern@google.com pull the latest from libwebp. Original source: <a href="http://git.chromium.org/webm/libwebp.git" rel="nofollow noreferrer noopener" target="_blank">http://git.chromium.org/webm/libwebp.git</a> 100644 blob 264210ba2807e4da47eb5d18c04cf869d89b9784 src/utils/thread.c commit 46fd44c1042c9903b2f1ab87e9f200a13c7e702d Author: James Zern <jzern@google.com> Date: Tue Jul 8 19:53:28 2014 -0700 thread: remove harmless race on status_ in End() if a thread was still doing work when End() was called there'd be a race on worker->status_. in these cases, however, the specific value is meaningless as it would be >= OK and the thread would have been shut down properly, but we'll check 'impl_' instead to avoid any potential TSan/DRD reports. Change-Id: Ib93cbc226a099f07761f7bad765549dffb8054b1 Change-Id: Ib0ef25737b3c6d017fa74822e21ed58508230b91 https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/1226d133df86e0bea6f89e9f0d86a77a8989999b Merge "Refactor vp9_diamond_search_sad function" 2014-07-10T11:06:32-07:00 Yunqing Wang yunqingwang@google.com https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/46441ec5c88529a9a3d4860d899992bf23e368e6 Merge "Refactor refining_search_sad code" 2014-07-10T10:43:00-07:00 Yunqing Wang yunqingwang@google.com https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/51e9788e58eb588f1cf89226a514e824e9e63d3b Fix a bug in boundary checking. 2014-07-10T09:43:04-07:00 hkuang hkuang@google.com Change-Id: Ifc741da9da6f61c8d3c1f675ec6b8a96570f877d https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/75cd57503d022d9c368f9b44f3568319ea8302dd Refactor vp9_diamond_search_sad function 2014-07-10T09:19:03-07:00 Yunqing Wang yunqingwang@google.com Currently, vp9_diamond_search_sadx4() is only called when sse3 is enabled, which is improper since sse2 optimization of sdx4df functions are available. Changed to always use vp9_diamond_search_sadx4(). Change-Id: I4b95d6b7a3c6c645783c373f0ba8d645ece24717 https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/2d8339eeabf9806a6f487a331761894eede253d6 Merge "vp9_decoder_remove: destroy common after thread shutdown" 2014-07-09T17:46:42-07:00 James Zern jzern@google.com https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/30117a576dc1590d95d840bb90f95e57277a0c9d Refactor refining_search_sad code 2014-07-09T16:50:11-07:00 Yunqing Wang yunqingwang@google.com There are sse2 optimization of sdx4df functions. Instead of calling vp9_refining_search_sadx4 only when sse3 is enabled, call it always. Change-Id: I24f93818f7d4209d1425039e0eb099ff9ff08fe9 https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/87cf002e9d8c3cb343dca706477adbefd14d0f83 Minor cleanup 2014-07-09T15:42:10-07:00 Yaowu Xu yaowu@google.com Change-Id: I3a3ceeeed489f8b1ccd7199ff97f3fb991bbf5a4 https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/a581da218e56fa9c1b2d72d124056ed412549edd Remove repetitive code in mcomp.c 2014-07-09T14:50:50-07:00 Yunqing Wang yunqingwang@google.com Deleted vp9_find_best_sub_pixel_comp_tree(), and combined it in vp9_find_best_sub_pixel_tree(). Change-Id: Ifb25763c8b19822df5537cc1daa76ce88dc3b056 https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/a51e389b426d69f920dad77f4a30a6ff5187306c Merge "Adjust full-pixel search method in real-time mode" 2014-07-09T13:46:42-07:00 Yunqing Wang yunqingwang@google.com https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/0e99f3a3873594d56e875f1181d5b3b86ed551c7 Merge "Combined non-rd motion searchs into a single function" 2014-07-09T13:02:25-07:00 Yaowu Xu yaowu@google.com https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/9bd3be69a447766780e6164ad69eda8b7d0a266f Adjust full-pixel search method in real-time mode 2014-07-09T12:56:25-07:00 Yunqing Wang yunqingwang@google.com Use FAST_HEX in speed 5 and 6, which covers more points than FAST_DIAMOND and improves motion search quality. At speed 6, RTC set borg tests showed slight quality gain (psnr gain: 0.143%, ssim gain: 0.226%). No noticeable encoding speed change. Change-Id: Ifa62875d9a52ee382ec494f271382bb77d8c67bf https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/c788bceb553c2d15e964160752a3afd80522b70b Combined non-rd motion searchs into a single function 2014-07-09T12:07:52-07:00 Yaowu Xu yaowu@google.com This commit combined the full pel and sub pel motion search into a single function to avoid code duplication. The commit does not change encoder outputs. Change-Id: Ibe18342c4f64073bef20f9cf6c6ca0a20d01bf0d https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/f6bf614b2f77616e00d34a2503aa7d2bed4b61de Merge "Re-design quantization process for 32x32 transform block" 2014-07-09T11:55:26-07:00 Jingning Han jingning@google.com https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/2e0588bc46b073d8bf65600facdcb31d6876d531 vp9_decoder_remove: destroy common after thread shutdown 2014-07-09T11:08:06-07:00 James Zern jzern@google.com in a failure case the threads may still be running and share a reference to VP9_COMMON Change-Id: I867034b4b55f133663b8cbf6ca06e72acf952849 https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/b84ee5a3d07a569968dc4fdf9c9d8d3bea155bd7 Merge "Move vp9_thread.* to common." 2014-07-09T10:16:13-07:00 hkuang hkuang@google.com https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/3008da9dea010ea9a7226fd5e6be67ca43afcfcf Merge "Vp9 denoiser MC bugfix" 2014-07-09T08:02:20-07:00 Tim Kopp tkopp@google.com https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/75e5abe83d2c3e7a6b453cb5537d4772565500a0 Merge "Fix decoder handling of intra-only frames" 2014-07-09T07:37:28-07:00 Adrian Grange agrange@google.com https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/84daeb5ea8c0f3959a675f2b046b6ab968eb42fc Merge "vp9_cx_iface.c: allow speed greater than 7" 2014-07-09T04:21:19-07:00 Guillaume Martres smarter3@gmail.com https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/8abbd37d21b0e15b3a3120685e3819dc2ac70f09 Merge changes I2abd6716,I4a65f7f8 2014-07-08T19:01:39-07:00 James Zern jzern@google.com * changes: cpu_speed_test: cosmetics aq_segment_test: cosmetics https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/bdfb9e580402a6153a7ce7cc3ab18a6f5f11375f Merge "invalid_file_test: output error detail on mismatch" 2014-07-08T19:00:53-07:00 James Zern jzern@google.com https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/9ad1b9fc67921cfaf58ed85732ed139530edab4a Re-design quantization process for 32x32 transform block 2014-07-08T16:55:28-07:00 Jingning Han jingning@google.com This commit enables a new quantization process for 32x32 2D-DCT transform coefficient blocks. It improves the compression performance of speed 5 by 1.4%. The overall compression gains of speed 5 due to the new quantization scheme is 4.7%. It also includes the SSSE3 implementation of the 32x32 quantization process. Change-Id: I0855b124fd6462418683f783f5bcb44255c9993b https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/7c43fb67ae5f8cd3ca39756281f63cc9e29bdb55 Fix decoder handling of intra-only frames 2014-07-08T16:24:03-07:00 Adrian Grange agrange@google.com This patch fixes bug 633: <a href="https://code.google.com/p/webm/issues/detail?id=633" rel="nofollow noreferrer noopener" target="_blank">https://code.google.com/p/webm/issues/detail?id=633</a> The first decoded frame does not have to be a keyframe, it could be an inter-frame that is coded intra-only. This patch fixes the handling of intra-only frames. A test vector has also been added that encodes 3 intra-only frames at the start of the clip. The test vector was generated using the code in the following patch: <a href="https://gerrit.chromium.org/gerrit/#/c/70680/" rel="nofollow noreferrer noopener" target="_blank">https://gerrit.chromium.org/gerrit/#/c/70680/</a> Change-Id: Ib40b1dbf91aae2bc047e23c626eaef09d1860147 https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/3c86228cd3c34acf7473c5c9273871c03d85e2b1 Vp9 denoiser MC bugfix 2014-07-08T15:13:13-07:00 Tim Kopp tkopp@google.com In the previous version, only certain buffers in the macroblockd were saved and the restored. In this version, all of the buffers are saved and restored. The code was then rolled into a loop for readability. Also contains a tiny fix for when the -DOUTPUT_YUV_DENOISED flag is used. Change-Id: Id925ef8b3fa122ae88acfa1d9a1e4df45df83518 https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/8c03fff40b05fa231adf8b564de22f03e42814b7 Move abs() to where it is effective 2014-07-08T14:06:33-07:00 Johann johannkoenig@google.com vp8/encoder/x86/denoising_sse2.c:35:10: error: taking the absolute value of unsigned type 'unsigned int' has no effect [-Werror,-Wabsolute-value] Change-Id: I749ba8e6f55dbd9b822bfd4260a8397554f5e524 https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/113dbf8d1e4fc7c2ce39f7b902c31d5c0b47a5ce vp9_cx_iface.c: allow speed greater than 7 2014-07-08T15:58:42+02:00 Guillaume Martres smarter3@gmail.com This makes it possible to use --rt --cpu-used=8. Change-Id: I8b5bc4449b6e05d24d25145e35b4793501268c59 https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/c0061cc24f254d648737986ce14ac1a4bcb45874 Merge "Fix build for examples/vp8_multi_resolution_encoder." 2014-07-07T17:07:13-07:00 Marco Paniconi marpan@google.com https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/5f732c2031549ee9bf546b88335fda7633b7a9d0 Fix build for examples/vp8_multi_resolution_encoder. 2014-07-07T16:59:07-07:00 Marco Paniconi marpan@google.com Change-Id: I7ec4e0e05487fe80d93e31e0f6a21f326b5c7276 https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/fe4b663559eb244b69faa8dbc7c9e75de06845ff Merge "Use the VP9 version of extend_borders" 2014-07-07T15:20:37-07:00 Johann johannkoenig@google.com https://gitlab.xiph.org/xiph/aom-rav1e/-/commit/337e8015c9deaf8ab7e8d0c3c132160a77dd1590 Move vp9_thread.* to common. 2014-07-07T14:52:19-07:00 hkuang hkuang@google.com Prepare for frame parallel decoding, the reference count buffers need to be protected by mutex. Move vp9_thread.* to common folder so that those buffers could use cross-platform mutex from vp9_thread.*. Change-Id: I541277cf15eefed6641555944f67f4a0bcdc8154
|
{
"url": "https://gitlab.xiph.org/xiph/aom-rav1e/-/commits/1b5e9871f7a4fe7b89da047df046b0cfb4b3566d?format=atom",
"source_domain": "gitlab.xiph.org",
"snapshot_id": "crawl=CC-MAIN-2021-25",
"warc_metadata": {
"Content-Length": "31439",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:QRT7M75Z5HQUFOSX4BQI2DQSCBJBDRRB",
"WARC-Concurrent-To": "<urn:uuid:ee66a314-a63d-436e-b6fd-61ebf90dbcba>",
"WARC-Date": "2021-06-22T02:30:43Z",
"WARC-IP-Address": "140.211.166.4",
"WARC-Identified-Payload-Type": "application/atom+xml",
"WARC-Payload-Digest": "sha1:4W46P26SMDGKUBAT4QLR7BR7WJI7CAKO",
"WARC-Record-ID": "<urn:uuid:40b9ccc7-85d5-4b80-9ddf-699886c16439>",
"WARC-Target-URI": "https://gitlab.xiph.org/xiph/aom-rav1e/-/commits/1b5e9871f7a4fe7b89da047df046b0cfb4b3566d?format=atom",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:6af51cad-8425-4a3d-95a1-d5330e6f7948>"
},
"warc_info": "isPartOf: CC-MAIN-2021-25\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for June 2021\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-171.ec2.internal\r\nsoftware: Apache Nutch 1.18 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.2-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0
],
"line_end_idx": [
13112
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 13112,
"ccnet_original_nlines": 0,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.11861970275640488,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.023005029186606407,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.4464414119720459,
"rps_doc_frac_unique_words": 0.4829268157482147,
"rps_doc_mean_word_length": 10.541463851928711,
"rps_doc_num_sentences": 195,
"rps_doc_symbol_to_word_ratio": 0.001078360015526414,
"rps_doc_unigram_entropy": 5.783488750457764,
"rps_doc_word_count": 1025,
"rps_doc_frac_chars_dupe_10grams": 0.020731139928102493,
"rps_doc_frac_chars_dupe_5grams": 0.07329940050840378,
"rps_doc_frac_chars_dupe_6grams": 0.06719111651182175,
"rps_doc_frac_chars_dupe_7grams": 0.04571957141160965,
"rps_doc_frac_chars_dupe_8grams": 0.029060620814561844,
"rps_doc_frac_chars_dupe_9grams": 0.020731139928102493,
"rps_doc_frac_chars_top_2gram": 0.008329479955136776,
"rps_doc_frac_chars_top_3gram": 0.01915780082345009,
"rps_doc_frac_chars_top_4gram": 0.00527533981949091,
"rps_doc_books_importance": -1249.612548828125,
"rps_doc_books_importance_length_correction": -1249.612548828125,
"rps_doc_openwebtext_importance": -829.4612426757812,
"rps_doc_openwebtext_importance_length_correction": -829.4612426757812,
"rps_doc_wikipedia_importance": -615.470458984375,
"rps_doc_wikipedia_importance_length_correction": -615.470458984375
},
"fasttext": {
"dclm": 0.08267509937286377,
"english": 0.5069650411605835,
"fineweb_edu_approx": 1.9046529531478882,
"eai_general_math": 0.17360764741897583,
"eai_open_web_math": 0.3245770335197449,
"eai_web_code": 0.32849442958831787
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.4",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "621.3922",
"labels": {
"level_1": "Industrial arts, Technology, and Engineering",
"level_2": "Engineering",
"level_3": "Mechanical engineering and Machinery"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "4",
"label": "Analyze"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "4",
"label": "Code/Software"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "1",
"label": "Leftover HTML"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "6",
"label": "Content Listing"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "4",
"label": "Graduate/Expert Level"
},
"secondary": {
"code": "3",
"label": "Undergraduate Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-1,302,896,652,823,900,700
|
Configure Topic Subscriptions with JMS Connector
Topic subscriptions in JMS enable you to configure how the subscription behaves regarding the connection of consumers and how consumers interact.
The Anypoint Connector for JMS (JMS Connector) Consumer and On New Message operations manage topic subscriptions in the Consumer type field by selecting the Topic consumer configuration.
Configure Durable Subscriptions
Durable subscriptions enable you to receive messages published to the topic while the consumer is offline. The JMS provider stores messages sent or published to a topic, just as it would store messages sent to a queue. If another application has a Topic consumer configuration that uses the same connection, client ID, topic, and subscription name, the subscription reactivates, and the JMS provider delivers the published messages while the subscriber was inactive.
In the following example, you Topic consumer to Durable:
1. In Studio, select the Consume operation from your flow.
2. Set the Destination field to #[vars.destination].
3. Set the Consumer type field to Topic consumer.
4. Select the Durable option.
5. Set the Subscription name to SampleSub.
In the Consume operation screen
Figure 1. JMS Connector Topic Consumer Durable configuration
In the XML editor, the <jms:topic-consumer> and durable configurations look like this:
<jms:consume config-ref="JMS_config" destination="#[vars.destination]">
<jms:consumer-type>
<jms:topic-consumer durable="true" subscriptionName="SampleSub"/>
</jms:consumer-type>
</jms:consume>
Configure Shared Subscriptions
In a JMS spec 1.1 connection, a subscription to a topic cannot have more than one consumer at a time, meaning that the processing work of messages on a topic subscription cannot be shared, thereby limiting the scalability of the application. The JMS spec 2.0 connection removes this restriction and enables you to configure shared consumers on the same subscription.
In the following example, you set Topic consumer to Shared:
1. In Studio, select the Consume operation from your flow.
2. Set the Destination field to InvoiceEventsTopic.
3. Set the Consumer type field to Topic consumer:
4. Select the Shared option.
5. Set the Subscription name to ClusterSubscription.
In the Consume operation screen
Figure 2. JMS Connector Topic Consumer Shared configuration
In the XML editor, the <jms:topic-consumer> and shared configurations look like this:
<jms:listener config-ref="config" destination="InvoiceEventsTopic">
<jms:consumer-type>
<jms:topic-consumer shared="true" subscriptionName="ClusterSubscription"/>
</jms:consumer-type>
</jms:listener>
Configure No Local Subscriptions
There are cases in which you may not want to receive published messages to a topic by the same application. To prevent the consumer to receive published messages to a topic by the same connection, configure the Topic consumer field to No local. Consumers configured as no local can not be part of a shared subscription.
In the following example, you set Topic consumer to No local :
1. In Studio, select the Consume operation from your flow.
2. Set the Destination field to {notificationsChannel}.
3. Set the Consumer type field to Topic consumer:
4. Select the No local option.
In the Consume operation screen
Figure 3. JMS Connector Topic Consumer No local configuration
In the XML editor, the <jms:topic-consumer> and noLocal configurations look like this:
<jms:listener config-ref="config" destination="${notificationsChannel}">
<jms:consumer-type>
<jms:topic-consumer noLocal="true"/>
</jms:consumer-type>
</jms:listener>
|
{
"url": "https://docs.mulesoft.com/jms-connector/1.7/jms-topic-subscription",
"source_domain": "docs.mulesoft.com",
"snapshot_id": "crawl=CC-MAIN-2021-43",
"warc_metadata": {
"Content-Length": "68427",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:C7GBUSKO6QSG5D3BNAI2TSM5IF2GYLEH",
"WARC-Concurrent-To": "<urn:uuid:6ace4771-0f4b-4cef-a894-b9f9d598dbea>",
"WARC-Date": "2021-10-21T11:45:51Z",
"WARC-IP-Address": "13.249.38.102",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:OK5K7ALAQ3J63457PCHJ75XTXHXRKVAH",
"WARC-Record-ID": "<urn:uuid:c88512c6-79ad-45ce-a572-8752854b6d85>",
"WARC-Target-URI": "https://docs.mulesoft.com/jms-connector/1.7/jms-topic-subscription",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:54f3f14a-d656-4644-9452-b8b12688da65>"
},
"warc_info": "isPartOf: CC-MAIN-2021-43\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for October 2021\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-180\r\nsoftware: Apache Nutch 1.18 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.2-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
49,
50,
196,
197,
384,
385,
417,
418,
885,
886,
943,
944,
1005,
1006,
1061,
1062,
1114,
1115,
1147,
1148,
1193,
1194,
1226,
1287,
1288,
1375,
1376,
1448,
1472,
1546,
1571,
1586,
1587,
1618,
1619,
1986,
1987,
2047,
2048,
2109,
2110,
2164,
2165,
2217,
2218,
2249,
2250,
2305,
2306,
2338,
2398,
2399,
2485,
2486,
2554,
2578,
2661,
2686,
2702,
2703,
2736,
2737,
3057,
3058,
3121,
3122,
3183,
3184,
3242,
3243,
3295,
3296,
3329,
3330,
3362,
3424,
3425,
3512,
3513,
3586,
3610,
3655,
3680
],
"line_end_idx": [
49,
50,
196,
197,
384,
385,
417,
418,
885,
886,
943,
944,
1005,
1006,
1061,
1062,
1114,
1115,
1147,
1148,
1193,
1194,
1226,
1287,
1288,
1375,
1376,
1448,
1472,
1546,
1571,
1586,
1587,
1618,
1619,
1986,
1987,
2047,
2048,
2109,
2110,
2164,
2165,
2217,
2218,
2249,
2250,
2305,
2306,
2338,
2398,
2399,
2485,
2486,
2554,
2578,
2661,
2686,
2702,
2703,
2736,
2737,
3057,
3058,
3121,
3122,
3183,
3184,
3242,
3243,
3295,
3296,
3329,
3330,
3362,
3424,
3425,
3512,
3513,
3586,
3610,
3655,
3680,
3695
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 3695,
"ccnet_original_nlines": 83,
"rps_doc_curly_bracket": 0.0010825400240719318,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.25035765767097473,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.021459229290485382,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.2575107216835022,
"rps_doc_frac_unique_words": 0.2947154641151428,
"rps_doc_mean_word_length": 5.890244007110596,
"rps_doc_num_sentences": 44,
"rps_doc_symbol_to_word_ratio": 0.0028612299356609583,
"rps_doc_unigram_entropy": 4.381933212280273,
"rps_doc_word_count": 492,
"rps_doc_frac_chars_dupe_10grams": 0.19116632640361786,
"rps_doc_frac_chars_dupe_5grams": 0.34161490201950073,
"rps_doc_frac_chars_dupe_6grams": 0.3333333432674408,
"rps_doc_frac_chars_dupe_7grams": 0.2632850110530853,
"rps_doc_frac_chars_dupe_8grams": 0.24189096689224243,
"rps_doc_frac_chars_dupe_9grams": 0.19116632640361786,
"rps_doc_frac_chars_top_2gram": 0.05383022874593735,
"rps_doc_frac_chars_top_3gram": 0.03933747112751007,
"rps_doc_frac_chars_top_4gram": 0.027605239301919937,
"rps_doc_books_importance": -314.72955322265625,
"rps_doc_books_importance_length_correction": -314.72955322265625,
"rps_doc_openwebtext_importance": -183.8176727294922,
"rps_doc_openwebtext_importance_length_correction": -183.8176727294922,
"rps_doc_wikipedia_importance": -179.0438690185547,
"rps_doc_wikipedia_importance_length_correction": -179.0438690185547
},
"fasttext": {
"dclm": 0.22710669040679932,
"english": 0.7664426565170288,
"fineweb_edu_approx": 2.181490182876587,
"eai_general_math": 0.3879941701889038,
"eai_open_web_math": 0.12668228149414062,
"eai_web_code": 0.3680257797241211
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.678",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "4",
"label": "Missing Images or Figures"
},
"secondary": {
"code": "0",
"label": "No missing content"
}
},
"document_type_v2": {
"primary": {
"code": "8",
"label": "Documentation"
},
"secondary": {
"code": "23",
"label": "Tutorial"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "3",
"label": "Mostly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "4",
"label": "Graduate/Expert Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
747,723,196,609,986,800
|
Answers
Solutions by everydaycalculation.com
Everydaycalculation.com » Answers » Divide fractions
Divide 5/12 with 7/36
5/12 ÷ 7/36 is 15/7.
Steps for dividing fractions
1. Find the reciprocal of the divisor
Reciprocal of 7/36: 36/7
2. Now, multiply it with the dividend
So, 5/12 ÷ 7/36 = 5/12 × 36/7
3. = 5 × 36/12 × 7 = 180/84
4. After reducing the fraction, the answer is 15/7
5. In mixed form: 21/7
MathStep (Works offline)
Download our mobile app and learn to work with fractions in your own time:
Android and iPhone/ iPad
Related:
© everydaycalculation.com
|
{
"url": "https://answers.everydaycalculation.com/divide-fractions/5-12-divided-by-7-36",
"source_domain": "answers.everydaycalculation.com",
"snapshot_id": "crawl=CC-MAIN-2019-47",
"warc_metadata": {
"Content-Length": "8218",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:LR4NTAPEBHKXOQ5F5CDG77YKYSMS2TRC",
"WARC-Concurrent-To": "<urn:uuid:02b74bff-6559-43eb-86da-8e82c0fb77f9>",
"WARC-Date": "2019-11-21T02:37:42Z",
"WARC-IP-Address": "96.126.107.130",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:BAUWSWPLQ6SJKCD3TUDOCTGC4FI4UTVR",
"WARC-Record-ID": "<urn:uuid:89fc5732-d9fc-41ec-b938-69c5125e28e6>",
"WARC-Target-URI": "https://answers.everydaycalculation.com/divide-fractions/5-12-divided-by-7-36",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:e7af3c8d-5058-48a9-a21e-60db0c065136>"
},
"warc_info": "isPartOf: CC-MAIN-2019-47\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for November 2019\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-5.ec2.internal\r\nsoftware: Apache Nutch 1.16 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.1-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
8,
9,
46,
47,
100,
101,
123,
124,
145,
146,
175,
176,
216,
245,
285,
319,
349,
402,
427,
428,
453,
454,
529,
554,
555,
564,
565
],
"line_end_idx": [
8,
9,
46,
47,
100,
101,
123,
124,
145,
146,
175,
176,
216,
245,
285,
319,
349,
402,
427,
428,
453,
454,
529,
554,
555,
564,
565,
590
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 590,
"ccnet_original_nlines": 27,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.1689189225435257,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.5540540218353271,
"rps_doc_frac_unique_words": 0.6774193644523621,
"rps_doc_mean_word_length": 4.623655796051025,
"rps_doc_num_sentences": 10,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 4.006186485290527,
"rps_doc_word_count": 93,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.027906980365514755,
"rps_doc_frac_chars_top_3gram": 0.0325581394135952,
"rps_doc_frac_chars_top_4gram": 0,
"rps_doc_books_importance": -34.63362503051758,
"rps_doc_books_importance_length_correction": -48.74824905395508,
"rps_doc_openwebtext_importance": -23.251405715942383,
"rps_doc_openwebtext_importance_length_correction": -37.366031646728516,
"rps_doc_wikipedia_importance": -34.204593658447266,
"rps_doc_wikipedia_importance_length_correction": -48.319217681884766
},
"fasttext": {
"dclm": 0.9693899750709534,
"english": 0.8384761810302734,
"fineweb_edu_approx": 2.5326383113861084,
"eai_general_math": 0.05294888839125633,
"eai_open_web_math": 0.3553098440170288,
"eai_web_code": -0.000008340000022144523
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "513.212",
"labels": {
"level_1": "Science and Natural history",
"level_2": "Mathematics",
"level_3": "Geometry"
}
},
"secondary": {
"code": "510",
"labels": {
"level_1": "Science and Natural history",
"level_2": "Mathematics",
"level_3": ""
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "1",
"label": "Factual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "23",
"label": "Tutorial"
},
"secondary": {
"code": "21",
"label": "Customer Support"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "4",
"label": "Highly Correct"
},
"secondary": {
"code": "5",
"label": "Exceptionally Correct"
}
},
"education_level": {
"primary": {
"code": "2",
"label": "High School Level"
},
"secondary": {
"code": "1",
"label": "General Audience"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
4,042,064,748,884,981,000
|
• Synthmeister
The fact that the developers program is too complex and costly? Nah.
The fact that the resulting games are too costly? Nah.
The fact that Sony went for proprietary tech like DMD, ATRAC and MemoryStick? Nah.
The fact that Sony didn’t have the sense to develop an iTunes-type store for at least its own music, movies, TV show catalog, not to mention games and other software, etc. without cumbersome DRM and with reasonable, low-cost media? Nah.
Did you see the article where the Sony exec boasted that development for the PS3 was intentionally cumbersome? That’s why Sony is in such a mess right now.
http://www.thatvideogameblog.com/2009/03/02/sony-made-ps3-a-pain-in-the-asson-purpose/
• kanada
Agreed with the top poster ^^^^^ the reason why the PSP and the PS3 are getting lacklustre sales is because Sony doesn’t support these systems well enough for people to buy them I own ONLY the ps3 and ONLY the PSP, I haven’t bought a new game for either in months the support just isn’t there. give me games, give me GOOD on line support, give me something to justify spending money on these systems. The Xbox 360 has a good library of games to play and it has good on line support to keep people coming back.
Sony has strong points with both systems, they just don’t exploit them enough.
• God™
I guess piracy is also killing the Nintendo DS?
Oh wait, it’s still selling like mad… how can this be?
This is a shame, as I have a PSP and really like it. I just wish they orginally included a better (refresh-wise) screen and dual analog sticks. These days I find myself playing on the iPhone more…
• Adam
It may be the type of games that it focuses on. From what I’ve experienced the psp focuses more on games that look and feel like they should be played on a full console, but sort of fails at this as (as well as many other reasons) people don’t tend to want to get into an in depth or time requiring game on a portable console (along with the loading time big games like this take). The DS on the other hand seems to focus on simple, fun, easy to just pick up and play type games (with little to no loading time) which in my opinion is probably what people want out of portable gaming, as by definition they would be playing on portable consoles while out and about to pass a small amount of time. I have both consoles. I don’t play either of them hardly ever as I am rarely out somewhere with time to spare, and when I’m at home i play (for lack of a better word) ‘proper’ games on my pc. When i first got my psp (years ago) I spent about £300 (GBP) on games over a year or so but almost every game sucked hard and i only played it a couple times before forgetting it (with the exception of burnout and loco roco, although they got boring after a month or so). After that i got fed up of wasting my money on crap games that i didn’t even play and took to downloading them, and i barely ever played a game more than once even then, so i gave up on the psp completely, but they got a good amount of my money by then and I think that’s fair. I would not buy a game that I’m not sure is good without trying out a downloaded copy first now, it costs too much money to try a game by buying it only to find out it sucks. I download many games now (pc and portable) but I also buy them retail when I find a game that is good and deserves the money, and some games (like GTA 4) I know will be good before buying it, so I just go out and buy them straight away.
• tech_ed
Wah! sony, Wah! Hey wake up sony…nobody wants your crap! Your PS3 is tanking, Blue ray is a miserable failure, and now your PSP can’t even be given away! Meanwhile, the Wii (which has a well published hack that will allow you to play any game loaded on an SD card with no hardware modifications what so ever) and the DS (which has over a dozen different manufacturers that make a hacked hardware card that allows anyone with internet access to download any Nindendo DS game they want and load it on their DS for free) are eating your lunch! Even Microsoft with it’s xbox that dies for mysterious causes (RRoD and now that mysterious e27 error) is making the PS3 look like a polished turd! Wake up Sony…it’s not piracy, its your inability to manage your own product…You are showing the world that if you build it, they will not necessarily come!You know…I’m a techno-holic and I feel no need to even look at Sony products. I get everything that sony makes from other manufacturers for less money and more features…And you know what? I’m glad you’re tanking. In fact it’s what I had always hoped for. Ever since Sony destroyed thousands of computers with their root kit, I’ve been preaching to everyone I know to stay away from the one and only company who believes that their customers are the enemy. Well guess what Sony, I *AM* your enemy…
• DWR
another giant problem with the PSP selling and to do with piracy is the fact that sony brought out the PSP then dropped the PS3 out right aftewwards so ppl dont want to blow money on games and stuff for the PSP cuz they rather have the PS3. let alone the prices of the games for the PSP. was online at walmart.com and looked up phantasy star portable which Sony has a demo but dont have a full game download yet and it was $39.94 (USD). sheesh I can go buy 10 original xbox games for that price and prolly play them 100 times longer. which explains alot on why piracy is so bad for the PSP. why pay $40 for a game when you can devolve your PSP and just get em free?
• soldier7
what the hell is sony talking about that their sale prices are going down yh its rite but there is one way that the sale prices can go up for gods sake if you cant beat ’em join ’em thats what sony should do exactly with the people who download games for people and here where i live u still have to pay 3 games for 0.500 KD thats around 1GBP how cheap is that?????!!!!!! sony if you ever read this dont complain about life. get the message LIFE ISINT FAIR cope with it and just join them!!!!!!!!!!!!!!!!!!!!!!!
|
{
"url": "http://www.geek.com/games/sony-says-that-piracy-is-killing-the-psp-750502/",
"source_domain": "www.geek.com",
"snapshot_id": "crawl=CC-MAIN-2015-35",
"warc_metadata": {
"Content-Length": "68700",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:VZHGEJWO2UEXGCQ7NNLU2H5VODDDFBEY",
"WARC-Concurrent-To": "<urn:uuid:b3fe2ea7-5869-4478-a2f1-c5210946280c>",
"WARC-Date": "2015-08-31T09:04:52Z",
"WARC-IP-Address": "172.232.11.176",
"WARC-Identified-Payload-Type": null,
"WARC-Payload-Digest": "sha1:ZA2G3KZBHH3ALSN5P7NBIDEFDUMH3XOA",
"WARC-Record-ID": "<urn:uuid:1f5ef70f-bb8c-497e-8f2a-7396ed772706>",
"WARC-Target-URI": "http://www.geek.com/games/sony-says-that-piracy-is-killing-the-psp-750502/",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:bf533943-689a-41e3-98d7-c8e84dc88e34>"
},
"warc_info": "robots: classic\r\nhostname: ip-10-171-96-226.ec2.internal\r\nsoftware: Nutch 1.6 (CC)/CC WarcExport 1.0\r\nisPartOf: CC-MAIN-2015-35\r\noperator: CommonCrawl Admin\r\ndescription: Wide crawl of the web for August 2015\r\npublisher: CommonCrawl\r\nformat: WARC File Format 1.0\r\nconformsTo: http://bibnum.bnf.fr/WARC/WARC_ISO_28500_version1_latestdraft.pdf"
}
|
{
"line_start_idx": [
0,
17,
18,
91,
150,
237,
478,
638,
729,
730,
741,
742,
1260,
1261,
1344,
1345,
1354,
1355,
1407,
1466,
1667,
1668,
1677,
1678,
3534,
3535,
3547,
3548,
4893,
4894,
4902,
4903,
5573,
5574,
5587,
5588
],
"line_end_idx": [
17,
18,
91,
150,
237,
478,
638,
729,
730,
741,
742,
1260,
1261,
1344,
1345,
1354,
1355,
1407,
1466,
1667,
1668,
1677,
1678,
3534,
3535,
3547,
3548,
4893,
4894,
4902,
4903,
5573,
5574,
5587,
5588,
6103
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 6103,
"ccnet_original_nlines": 35,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 1,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.4789977967739105,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.05011054128408432,
"rps_doc_frac_lines_end_with_ellipsis": 0.055555559694767,
"rps_doc_frac_no_alph_words": 0.1407516598701477,
"rps_doc_frac_unique_words": 0.4019349217414856,
"rps_doc_mean_word_length": 4.1319260597229,
"rps_doc_num_sentences": 54,
"rps_doc_symbol_to_word_ratio": 0.00589535990729928,
"rps_doc_unigram_entropy": 5.4812235832214355,
"rps_doc_word_count": 1137,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.013197110034525394,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.011494250036776066,
"rps_doc_frac_chars_top_3gram": 0.011707110330462456,
"rps_doc_frac_chars_top_4gram": 0.008939970284700394,
"rps_doc_books_importance": -702.8550415039062,
"rps_doc_books_importance_length_correction": -702.8550415039062,
"rps_doc_openwebtext_importance": -364.3211669921875,
"rps_doc_openwebtext_importance_length_correction": -364.3211669921875,
"rps_doc_wikipedia_importance": -268.9761047363281,
"rps_doc_wikipedia_importance_length_correction": -268.9761047363281
},
"fasttext": {
"dclm": 0.021878359839320183,
"english": 0.9650238752365112,
"fineweb_edu_approx": 0.9218924641609192,
"eai_general_math": 0.023106930777430534,
"eai_open_web_math": 0.09759914875030518,
"eai_web_code": 0.005176899954676628
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "004.67",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
},
"secondary": {
"code": "338.4",
"labels": {
"level_1": "Social sciences",
"level_2": "Economics",
"level_3": "Industries, Prices, and Microeconomics"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "5",
"label": "Evaluate"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "5",
"label": "Comment Section"
},
"secondary": {
"code": "16",
"label": "Personal Blog"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "6",
"label": "Not Applicable/Indeterminate"
},
"secondary": {
"code": "2",
"label": "Partially Correct"
}
},
"education_level": {
"primary": {
"code": "1",
"label": "General Audience"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-3,690,611,531,124,368,000
|
Android: Convertir URLs en enlaces dentro de un TextView
septiembre 8, 2017
Si el texto que vamos a mostrar en un TextView contiene código HTML, se visualizarán correctamente los enlaces, negritas, etc. Deberemos hacerlo de así desde código: textView1.setText( Html.fromHtml("Mi <strong>página web</strong>: " + "<a href="http://jonsegador.com">http://jonsegador.com</a>") );textView1.setText( Html.fromHtml("Mi <strong>página web</strong>: " + "<a href="http://jonsegador.com">http://jonsegador.com</a>") ); En cambio, si el texto no está en formato HTML pero contiene URLs (sin las etiquetas <a>), podemos convertir a enlace cualquier URL que aparezca en el ...
Butter Knife: librería para inyectar views (vistas) en Android
noviembre 16, 2015
Butter Knife es una librería que nos facilitará la tarea de relacionar los elementos de las vistas con el código en nuestras aplicaciones Android. Nos evitará tener que utilizar findViewById y simplificará el código. Lo vemos más fácil con un ejemplo. Tenemos un layout llamado main_activity.xml con la siguiente estructura: 1 2 3 4 5 6 7 8 9 10 11 <?xml version="1.0" encoding="utf-8"?> <LinearLayout xmlns:android="http://schemas.android.com/apk/res/android" android:layout_width="match_parent" android:layout_height="match_parent" android:orientation="vertical"> <TextView ...
Acceder a la carpeta «data» de una aplicación Android
enero 14, 2015
En una aplicación Android podemos guardar la información que generamos en la app (imágenes, archivos, etc.) en la tarjeta SD del dispositivo o en la propia carpeta interna de la aplicación (y no podremos consultar esa información desde fuera de la app). Por ejemplo, imaginemos que queremos desarollar una aplicación Android en la que podemos hacer fotos pero que solo se pueden utilizar desde la propia app. No queremos que ...
Firmar aplicación Android sin utilizar Eclipse o Android Studio
noviembre 26, 2014
Para subir una aplicación a Google Play es obligatorio que esté firmada. Si estamos desarrollando una aplicación para nosotros mismos o para nuestra empresa, el propio Eclipse o Android Studio nos ofrecen la posibilidad de exportar la aplicación ya firmada. En el supuesto de este artículo, estamos desarrollando una aplicación para un cliente o hemos contratado a alguien externo para que nos programe la aplicación. En este caso, no queremos ...
Popup para ir a valorar la aplicación en Google Play [Android]
enero 14, 2013
Sabemos lo importante que es que nuestra aplicación Android sea valorada por nuestros usuarios en Google Play para conseguir más descargas, aparecer antes en los resultados de búsqueda, etc. Es una costumbre habitual que una aplicación sea valorada solamente si hemos tenido una mala experiencia con ella (nos darán una estrella) y son los menos los que la valoran positivamente si les ha gustado (así somos 🙁 ). Una forma ...
Mostrar pantalla splash en Android durante unos segundos al iniciar la aplicación
noviembre 20, 2012
Cuando iniciamos una aplicación en nuestro dispositivo Android, es habitual que se muestre durante unos pocos segundos una pantalla inicial (también llamada «splash«) donde se muestra el logotipo de la aplicación, de la empresa, etc. También es habitual utilizar esta pantalla para la precarga de datos y así tenerlos disponibles una vez la aplicación haya iniciado. En este post vamos a ver como mostrar una pantalla splash durante unos segundos ...
|
{
"url": "https://jonsegador.com/category/android/",
"source_domain": "jonsegador.com",
"snapshot_id": "crawl=CC-MAIN-2021-21",
"warc_metadata": {
"Content-Length": "44744",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:AIQTM62BJBO5PLJ7OYTWOAGAHWAZIWLC",
"WARC-Concurrent-To": "<urn:uuid:5835db17-ae9d-4736-8250-7f6421b15e0d>",
"WARC-Date": "2021-05-17T03:29:22Z",
"WARC-IP-Address": "185.118.56.135",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:DD34K2JVEIMLS3FIW7WYBYREI7X6U67D",
"WARC-Record-ID": "<urn:uuid:0ff88586-deee-443e-8987-c5a392312998>",
"WARC-Target-URI": "https://jonsegador.com/category/android/",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:429bf186-f545-4243-9740-0b247a1048b4>"
},
"warc_info": "isPartOf: CC-MAIN-2021-21\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for May 2021\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-224.ec2.internal\r\nsoftware: Apache Nutch 1.18 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.2-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
57,
58,
77,
78,
666,
667,
730,
731,
750,
751,
1331,
1332,
1386,
1387,
1402,
1403,
1832,
1833,
1897,
1898,
1917,
1918,
2366,
2367,
2430,
2431,
2446,
2447,
2874,
2875,
2957,
2958,
2977,
2978
],
"line_end_idx": [
57,
58,
77,
78,
666,
667,
730,
731,
750,
751,
1331,
1332,
1386,
1387,
1402,
1403,
1832,
1833,
1897,
1898,
1917,
1918,
2366,
2367,
2430,
2431,
2446,
2447,
2874,
2875,
2957,
2958,
2977,
2978,
3428
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 3428,
"ccnet_original_nlines": 34,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.08132530003786087,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.006024099886417389,
"rps_doc_frac_lines_end_with_ellipsis": 0.17142857611179352,
"rps_doc_frac_no_alph_words": 0.23644578456878662,
"rps_doc_frac_unique_words": 0.48065173625946045,
"rps_doc_mean_word_length": 5.631364345550537,
"rps_doc_num_sentences": 34,
"rps_doc_symbol_to_word_ratio": 0.009036139585077763,
"rps_doc_unigram_entropy": 4.992251873016357,
"rps_doc_word_count": 491,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.09403254836797714,
"rps_doc_frac_chars_dupe_6grams": 0.06654611229896545,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.040506329387426376,
"rps_doc_frac_chars_top_3gram": 0.02278481051325798,
"rps_doc_frac_chars_top_4gram": 0.03761301934719086,
"rps_doc_books_importance": -321.0212707519531,
"rps_doc_books_importance_length_correction": -321.0212707519531,
"rps_doc_openwebtext_importance": -148.84121704101562,
"rps_doc_openwebtext_importance_length_correction": -148.84121704101562,
"rps_doc_wikipedia_importance": -143.95872497558594,
"rps_doc_wikipedia_importance_length_correction": -143.95872497558594
},
"fasttext": {
"dclm": 0.7190334796905518,
"english": 0.0016598999500274658,
"fineweb_edu_approx": 1.0207973718643188,
"eai_general_math": 0.00006294000195339322,
"eai_open_web_math": 0.6830654740333557,
"eai_web_code": 0.4789958596229553
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "004.0285",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computers and Computer science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "1",
"label": "Truncated Snippets"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "23",
"label": "Tutorial"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
5,333,130,138,929,024,000
|
Over a million developers have joined DZone.
{{announcement.body}}
{{announcement.title}}
The Continuous Delivery Challenge in the Enterprise
DZone's Guide to
The Continuous Delivery Challenge in the Enterprise
Learn about the unique challenges for continuous delivery presented by the added complexity of an enterprise context.
· DevOps Zone ·
Free Resource
DevOps involves integrating development, testing, deployment and release cycles into a collaborative process. Learn more about the 4 steps to an effective DevSecOps infrastructure.
Continuous delivery (CD) as an engineering practice is taking hold at enterprises everywhere. Most forward-looking app developers' efforts rely on CD to one extent or another. Typically, that is in the form of a functionally automated pipeline for code promotion and some test execution. Some amount of the delivery work, such as database changes, provisioning or configuration management tickets, production signoffs, etc., is still done manually. These forward-looking teams, therefore, have a CD pipeline that "works" reasonably well.
There is an old engineering adage that accurately describes the attitude many such teams have towards adopting CD: "First, make it work. Then, make it work well. Finally, make it work quickly and efficiently." Today, enterprises are getting through the first and second phases of that adage in their CD adoption efforts, but they are going to want to reach the third eventually-and that's where the difficulty lies. Organizations in this position should start planning for phase three now to avoid the expense and disruption of bringing it under control later down the line.
A Pipeline of Pipelines
Enterprises attempting to transform their app delivery approaches typically rely on team-level efforts. As a result, they usually have app delivery pipelines in different areas of the business. Many of those current efforts have a very limited scope, only focusing on the basic functional tasks of the specific technical environments of the specific application system they support. Sometimes the focus may even just be on a subset of those environments. Furthermore, the pipelines are often duplicative of each other across teams-even if the technology stacks are the same. There is nothing but manual effort and spreadsheets coordinating the pipelines.
This is a result of teams' natural, but narrow, focus on their functional needs. The narrow focus can create architectural problems when it comes to helping adjacent delivery pipelines-especially if the tech stacks among the adjacent teams are different. That is because most team-level tools do not support the variety of tech stacks present in many enterprises. As a result, these function-focused automated pipelines still rely on manual management techniques for higher-level needs, such as cross-app dependency management. These enterprise needs are less technically focused or have other, larger business aspects that are beyond the scope of a team's responsibility-even if the team's activities impact those needs.
As development teams build out newer applications that expand to become critical pieces of enterprise software infrastructure, they discover that they now need something to manage their "pipeline of pipelines." No matter how consistently the involved teams' individual pipelines work, their narrow focus limits visibility and constrains their ability to effectively manage complexity for the business stakeholders. That blinds business stakeholders to the progress of key features and defects and is exacerbated when there are dependent projects. Existing data reported by team-level tools does not help (and may even hinder) coordination, security, quality, or compliance efforts, because the data resides in so many formats and tools across the various teams that it is impossible to correlate.
Enterprise-Grade Continuous Delivery Solutions
So, how do enterprises progress from scattered CD pipelines that merely "work" to CD pipelines that "work quickly and efficiently" at the scale they require? They switch to a model-driven approach that enables them to leverage the functional effectiveness of team-level efforts and, without throwing those away, thread them into a coherent and manageable whole. These models — a hallmark of enterprise-grade CD tools — enable enterprises to gain a clear, end-to-end understanding of complex value streams at both the technical "works" level and the management "works quickly and efficiently" level.
A model-driven approach to bringing disparate team efforts together:
• Eases coordination among dependencies by supporting heterogeneity in tools and team preferences and supporting the breadth of enterprise technology equally (containers, cloud, platforms, legacy distributed, mainframe)
• Increases visibility by providing a broad framework that collects data (both statistical and business-stakeholder relevant, e.g. feature/defect progress, etc.) for coherent reporting to the business and management
• Improves security by providing a consistent framework for enterprise security and compliance concerns, managed consistently for all teams with minimal duplication
The emerging awareness that CD requires different or additional tools to manage the complexity in an enterprise context is a natural outcome of the constantly evolving modernization of software delivery practices. It is an example of why CD practitioners and evangelists talk about the adoption of such practices as a "journey". With that journey will come learnings that shift team managers from being excited that something works "well" to an urgency toward taking the next step on their journey to make them "work quickly and efficiently."
Read the 4-part DevOps testing eBook to learn how to detect problems earlier in your DevOps testing processes.
Topics:
devops ,automation ,continuous delivery ,enterprise
Published at DZone with permission of
Opinions expressed by DZone contributors are their own.
{{ parent.title || parent.header.title}}
{{ parent.tldr }}
{{ parent.urlSource.name }}
|
{
"url": "https://dzone.com/articles/the-continuous-delivery-challenge-in-the-enterpris?fromrel=true",
"source_domain": "dzone.com",
"snapshot_id": "crawl=CC-MAIN-2019-13",
"warc_metadata": {
"Content-Length": "151468",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:LAPLR3RERMJDPFTOZHGXEFBLTAPFB4AB",
"WARC-Concurrent-To": "<urn:uuid:d9690721-d688-471f-afb6-94dbd061ab30>",
"WARC-Date": "2019-03-21T01:25:55Z",
"WARC-IP-Address": "3.86.134.213",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:WZ7LT36IDQP2V4KGSXV5QVFYLDVQFTCE",
"WARC-Record-ID": "<urn:uuid:8f984a47-f7ae-4927-b29a-d709d591ebbc>",
"WARC-Target-URI": "https://dzone.com/articles/the-continuous-delivery-challenge-in-the-enterpris?fromrel=true",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:0e7e5d9c-b5b3-49d6-ae96-410df2a7dc57>"
},
"warc_info": "isPartOf: CC-MAIN-2019-13\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for March 2019\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-143-92-167.ec2.internal\r\nsoftware: Apache Nutch 1.15 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 0.11-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
45,
67,
90,
91,
143,
144,
161,
162,
214,
215,
333,
334,
350,
364,
365,
546,
547,
1085,
1086,
1661,
1662,
1686,
1687,
2342,
2343,
3065,
3066,
3863,
3864,
3911,
3912,
4511,
4512,
4581,
4582,
4804,
5022,
5189,
5190,
5733,
5734,
5845,
5846,
5854,
5906,
5907,
5945,
5946,
6002,
6003,
6044,
6045,
6063,
6064
],
"line_end_idx": [
45,
67,
90,
91,
143,
144,
161,
162,
214,
215,
333,
334,
350,
364,
365,
546,
547,
1085,
1086,
1661,
1662,
1686,
1687,
2342,
2343,
3065,
3066,
3863,
3864,
3911,
3912,
4511,
4512,
4581,
4582,
4804,
5022,
5189,
5190,
5733,
5734,
5845,
5846,
5854,
5906,
5907,
5945,
5946,
6002,
6003,
6044,
6045,
6063,
6064,
6091
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 6091,
"ccnet_original_nlines": 54,
"rps_doc_curly_bracket": 0.003283530008047819,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.3712686598300934,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.011194029822945595,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.15485075116157532,
"rps_doc_frac_unique_words": 0.459090918302536,
"rps_doc_mean_word_length": 5.684091091156006,
"rps_doc_num_sentences": 50,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 5.44345760345459,
"rps_doc_word_count": 880,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.01799280010163784,
"rps_doc_frac_chars_dupe_6grams": 0.01799280010163784,
"rps_doc_frac_chars_dupe_7grams": 0.01799280010163784,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.02159135974943638,
"rps_doc_frac_chars_top_3gram": 0.016793280839920044,
"rps_doc_frac_chars_top_4gram": 0.0149940000846982,
"rps_doc_books_importance": -400.4898681640625,
"rps_doc_books_importance_length_correction": -400.4898681640625,
"rps_doc_openwebtext_importance": -265.3407287597656,
"rps_doc_openwebtext_importance_length_correction": -265.3407287597656,
"rps_doc_wikipedia_importance": -207.10574340820312,
"rps_doc_wikipedia_importance_length_correction": -207.10574340820312
},
"fasttext": {
"dclm": 0.06110328063368797,
"english": 0.9415856003761292,
"fineweb_edu_approx": 1.6988528966903687,
"eai_general_math": 0.15683633089065552,
"eai_open_web_math": 0.11602497100830078,
"eai_web_code": 0.3085319995880127
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.452",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "658.4038",
"labels": {
"level_1": "Industrial arts, Technology, and Engineering",
"level_2": "Business",
"level_3": "Management"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "2",
"label": "Understand"
},
"secondary": {
"code": "3",
"label": "Apply"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "1",
"label": "Leftover HTML"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "10",
"label": "Knowledge Article"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
-5,920,912,024,613,307,000
|
Taschenrechner mit Visual Basic
Diese Seite verwendet Cookies. Durch die Nutzung unserer Seite erklären Sie sich damit einverstanden, dass wir Cookies setzen. Weitere Informationen
Unsere Datenschutzerklärung wurde aktualisiert. Mit der Nutzung unseres Forums akzeptierst Du unsere Datenschutzerklärung. Du bestätigst zudem, dass Du mindestens 16 Jahre alt bist.
• Taschenrechner mit Visual Basic
Hi an alle. ich mache gerade ein Praktikum als Fachinformatiker. Ich hab heut damit anfangen müssen, einen taschenrechner mit visual basic zu programmieren. ich hab schon ein bisschen erfahrung in dem programm.
ich hab jetz mal angefangen mit dem aussehen, und hab den tasten schon funktionen hinzugefügt. also, dass wenn man z.b. auf 1 klickt, dass es in einem textfeld auch 1 hinschreibt, usw. und jetz hab ich leider keine ahnung, wie man den taschenrechner dazu bringt, dass er sich die zahlen merkt und, dass er es auch noch ausrechnet. wär echt nett, wenn mir jemand helfen könnte
ps: es reicht, wenn die Addition funktioniert
so sieht mein taschenrechner aus:
[Blockierte Grafik: http://img44.imageshack.us/img44/3421/19574903.jpg]
und so sieht mein Quelltext bis jetzt aus:
Private Sub cb_g_Click() 'teilen zeichen
End Sub
Private Sub cb_i_Click() '"Ist gleich" zeichen
End Sub
Private Sub cb_m_Click() 'mal zeichen
End Sub
Private Sub cb_mi_Click() 'minus zeichen
End Sub
Private Sub cb_p_Click() 'plus zeichen
End Sub
Private Sub cb0_Click() 'Ziffer 0
Label1.Caption = 0
End Sub
Private Sub cb1_Click() 'Ziffer 1
Label1.Caption = 1
End Sub
Private Sub cb2_Click() 'Ziffer 2
Label1.Caption = 2
End Sub
Private Sub cb3_Click() 'Ziffer 3
Label1.Caption = 3
End Sub
Private Sub cb4_Click() 'Ziffer 4
Label1.Caption = 4
End Sub
Private Sub cb5_Click() 'Ziffer 5
Label1.Caption = 5
End Sub
Private Sub cb6_Click() 'Ziffer 6
Label1.Caption = 6
End Sub
Private Sub cb7_Click() 'Ziffer 7
Label1.Caption = 7
End Sub
Private Sub cb8_Click() 'Ziffer 8
Label1.Caption = 8
End Sub
Private Sub cb9_Click() 'Ziffer 9
Label1.Caption = 9
End Sub
Private Sub Label1_Click() 'Textfeld
End Sub
bitte ich brauch hilfe...
danke schonmal im vorraus
• Hallo Tequila99,
da ich mit meinem neuen Laptop Vista fahre ist mir der Zugang zu Visual Basic 6 leider nicht mehr möglich.
Habe das Problem mir mal unter VBA durch den Kopf gehen lassen und für eine einfache Addition folgen Code durchgespielt (funktioniert musst Du aber auf Deinen Code anpassen).
Wie gewünscht ein Beispiel für die Addition von zwei Zahlen.
' ------------------------------------------------------------------
Dim ZahlMerker As Integer ' wird benötigt um die 1.Zahl zu merken
Dim RechMerker As String ' wird benötigt um die Rechenart zu merken
' ------------------------------------------------------------------
Private Sub cmd3_Click()
lbl1.Caption = "3"
End Sub
' ---------------------------------------------------------
Private Sub cmd1_Click()
lbl1.Caption = "1"
End Sub
' ---------------------------------------------------------
Private Sub cmd2_Click()
lbl1.Caption = "2"
End Sub
' ---------------------------------------------------------
Private Sub cmd4_Click()
lbl1.Caption = "4"
End Sub
' ---------------------------------------------------------
Private Sub cmd5_Click()
lbl1.Caption = "5"
End Sub
' ---------------------------------------------------------
Private Sub cmd6_Click()
lbl1.Caption = "6"
End Sub
' ---------------------------------------------------------
Private Sub cmd7_Click()
lbl1.Caption = "7"
End Sub
' ---------------------------------------------------------
Private Sub cmd8_Click()
lbl1.Caption = "8"
End Sub
' ---------------------------------------------------------
Private Sub cmd9_Click()
lbl1.Caption = "9"
End Sub
' ---------------------------------------------------------
Private Sub cmdGleich_Click()
Select Case RechMerker
Case "+"
lbl1.Caption = ZahlMerker + Val(lbl1.Caption)
End Select
End Sub
' ---------------------------------------------------------
Private Sub cmdplus_Click()
ZahlMerker = Val(lbl1.Caption)
RechMerker = "+"
lbl1.Caption = ""
End Sub
Wenn ich Dir damit helfen konnte, bitte schön.
Gruß
Sascha
Wer ein Problem erkennt, und nichts zu seiner Beseitigung unternimmt, der ist möglicherweise ein Teil dieses Problems.:D
• Hallo liebe Community :p
Erstmal ein Nasenrümpfer :evil:
Dein Vorgestellter Code ist als solcher nicht vorhanden,schöner wäre es gewesen wenn du einen Ansatz fomuliert hättest und zur Ergänzung dann in einem Forum fragst !
Hier mal ein Ansatz mit Excel 2000 VB,du weisst das das ein größeres Projekt ist und mindestens 1-2 Tage intensivste Arbeit erfordert(bei Profis) :?:
Habe jetzt schon festgestellt das die Fehlerroutine das größte Modul sein wird.
Liebe Grüße euer Tanto :p
Meine Idee dazu war, Zahlen wie Operanden jeweils zu Isolieren und in ein Array zu legen,beachte aber das Operanden auch vorangestellt werden dürfen,habe aber weitere Arbeit eingestellt,ist zu umfangreich ;-)
Quellcode
1. Sub Gleich()
2. ReDim DatZahlen(0) As String
3. ReDim DatOP(0) As String
4. 'prüfung auf falsche zeichen,auf mehrfache fehlt noch
5. For Zeichen = 1 To Len(Cells(4, 4))
6. If Mid(Cells(4, 4), Zeichen, 1) Like "0-9+-*/" = True Then
7. Lager = Lager + Cells(4, 4)
8. End If
9. Next Zeichen
10. For Zeichen = 1 To Len(Cells(4, 4))
11. 'Zahlen Isolieren
12. If Mid(Cells(4, 4), Zeichen, 1) Like "0-9" = True Then
13. DatZahlIndex = DatZahlIndex + 1
14. ReDim Preserve DatZahlen(DatZahlIndex)
15. DatZahlen(DatZahlIndex) = Mid(Cells(4, 4), Zeichen, 1)
16. End If
17. 'Operanden Isolieren
18. If Mid(Cells(4, 4), Zeichen, 1) Like "+-*/" = True Then
19. DatOpIndex = DatOpIndex + 1
20. ReDim Preserve DatOP(DatOpIndex)
21. DatOP(DatOpIndex) = Mid(Cells(4, 4), Zeichen, 1)
22. End If
23. Next Zeichen
24. For Zzahl = 1 To UBound(DatZahlen())
25. 'hier sollten jetzt die Felder miteinander Operieren
26. Next Zzahl
27. End Sub
Alles anzeigen
Quellcode
1. Sub Plus()
2. Cells(4, 4) = Cells(4, 4) & "+"
3. End Sub
Quellcode
1. Sub Minus()
2. Cells(4, 4) = Cells(4, 4) & "-"
3. End Sub
Quellcode
1. Sub Mal()
2. Cells(4, 4) = Cells(4, 4) & "*"
3. End Sub
Quellcode
1. Sub Geteilt()
2. Cells(4, 4) = Cells(4, 4) & "/"
3. End Sub
Noch einige Gedankengänge :-D
On Error Goto ErrorHandler/Über Functionen auslagern :-)
Operanden können vor/hinter angestellt sein(nicht vergessen) :cry:
Erstelle dir eine Liste mit möglichen Fehlern um gegebenenfalls zu korrigieren 8O
Vorrangig sind Einschränkungen statt Korrigierung ;-)
Viel spass bei dem Projekt :lol:
• ich möchte gern noch, dass der taschenrechner minus, mal, geteilt kann, ich möchte dafür aber nicht gleich einen ganz neuen code schreiben, sonder die funktion einfach hinzufügen.
so sieht es im moment aus
Quellcode
1. Dim ZahlMerker As String
2. Dim RechMerker As String
3. Dim Zahl1 As Double
4. Private Sub cb_0_Click() 'button 0
5. If ZahlMerker <> "" Then
6. ZahlMerker = ZahlMerker & "0"
7. Label1.Caption = ZahlMerker
8. End If
9. End Sub
10. Private Sub cb_1_Click() 'button 1
11. ZahlMerker = ZahlMerker & "1"
12. Label1.Caption = ZahlMerker
13. End Sub
14. Private Sub cb_2_Click() 'button 2
15. ZahlMerker = ZahlMerker & "2"
16. Label1.Caption = ZahlMerker
17. End Sub
18. Private Sub cb_3_Click() 'button 3
19. ZahlMerker = ZahlMerker & "3"
20. Label1.Caption = ZahlMerker
21. End Sub
22. Private Sub cb_4_Click() 'button 4
23. ZahlMerker = ZahlMerker & "4"
24. Label1.Caption = ZahlMerker
25. End Sub
26. Private Sub cb_5_Click() 'button 5
27. ZahlMerker = ZahlMerker & "5"
28. Label1.Caption = ZahlMerker
29. End Sub
30. Private Sub cb_6_Click() 'button 6
31. ZahlMerker = ZahlMerker & "6"
32. Label1.Caption = ZahlMerker
33. End Sub
34. Private Sub cb_7_Click() 'button 7
35. ZahlMerker = ZahlMerker & "7"
36. Label1.Caption = ZahlMerker
37. End Sub
38. Private Sub cb_8_Click() 'button 8
39. ZahlMerker = ZahlMerker & "8"
40. Label1.Caption = ZahlMerker
41. End Sub
42. Private Sub cb_9_Click() 'button 9
43. ZahlMerker = ZahlMerker & "9"
44. Label1.Caption = ZahlMerker
45. End Sub
46. Private Sub cb_c_Click() 'C taste, zum entfernen der eingabe
47. RechMerker = ""
48. ZahlMerker = ""
49. Ergebnis = ""
50. Label1.Caption = ""
51. Zahl1 = "0"
52. End Sub
53. Private Sub cb_k_Click() 'Komma button
54. ZahlMerker = ZahlMerker & "."
55. Label1.Caption = ZahlMerker
56. End Sub
57. Private Sub cb_p_Click() 'Plus button
58. Zahl1 = Val(ZahlMerker)
59. RechMerker = "+"
60. ZahlMerker = ""
61. End Sub
62. Private Sub cb_i_Click() '= button
63. Dim Ergebnis As Double
64. Select Case RechMerker
65. Case "+"
66. Ergebnis = Zahl1 + Val(ZahlMerker)
67. ZahlMerker = Ergebnis
68. Label1.Caption = Ergebnis
69. End Select
70. End Sub
Alles anzeigen
• @tequila99
Nachdem Du nun mit ein wenig Hilfe so weit gekommen bist sollte das für
Dich doch kein Problem mehr sein.
Dein Ergebnis (ob in einem Label oder einem Textfeld) liegt doch vor.
Nun nimmst Du Dein Ergebnis und rechnest weiter damit.
Das setzt natürlich voraus, dass Du die Zahl mit der neuen Eingabe nicht löscht.
:|Gruß
Sascha
Wer ein Problem erkennt, und nichts zu seiner Beseitigung unternimmt, der ist möglicherweise ein Teil dieses Problems.:D
• Hallo liebe Community :-D
Da hab ich ja noch was,vielleicht brauchbar :-)
Eine Function die Zahlenblöcke isoliert und einem Array übergibt ;-)
Die Functionsparameter dürften sich im Makro klären :!:
Liebe Grüße euer Tanto :p
Quellcode
1. Sub ZahlenIsolieren()
2. ReDim DatZahlen(0) As String
3. Dim AnzZahl As Integer
4. AnzZahl = 1
5. Do
6. 'Zum testen wird Cells(4, 4) genutzt,wie z.b. "10,7+3,1+3.333,33"
7. If SumZahlen(Cells(4, 4), AnzZahl) = "" Then
8. Exit Do
9. Else
10. DatZahlIndex = DatZahlIndex + 1
11. ReDim Preserve DatZahlen(DatZahlIndex)
12. DatZahlen(DatZahlIndex) = SumZahlen(Cells(4, 4), AnzZahl)
13. AnzZahl = AnzZahl + 1
14. End If
15. Loop
16. For Zzahl = 1 To UBound(DatZahlen())
17. 'Das Array ist nun mit einer X Anzahl an Zahlen die auch Punkt wie Komma beinhalten können gefüllt
18. 'Zum testen Cells(Zzahl, 1) = DatZahlen(Zzahl)
19. Next Zzahl
20. End Sub
Alles anzeigen
Quellcode
1. Function SumZahlen(Zellen As Variant, zaehler1 As Integer) As String
2. Dim Zelle As Range
3. Dim zeich1 As Integer
4. Dim schalter As Boolean
5. Dim zaehler3 As Integer
6. ReDim zaehler2(Len([Zellen])) As String
7. zaehler3 = 1
8. Application.Volatile
9. If zaehler1 > Len([Zellen]) Then zaehler1 = Len([Zellen])
10. For zeich1 = 1 To Len([Zellen])
11. If Mid([Zellen], zeich1, 1) Like "[0-9,.]" = True Then
12. zaehler2(zaehler3) = zaehler2(zaehler3) & Mid([Zellen], zeich1, 1)
13. schalter = True
14. End If
15. If schalter = True And Mid([Zellen], zeich1, 1) Like "[0-9,.]" = False Then
16. zaehler3 = zaehler3 + 1
17. schalter = False
18. End If
19. Next zeich1
20. SumZahlen = zaehler2(zaehler1)
21. End Function
Alles anzeigen
Die Function lässt sich auch leicht ändern um Operatoren zu isolieren :pc:
Ersetzen
Like "[0-9,.]"
Durch
Like "[+-*/]" und oder weitere Operatoren
• Hallo liebe Community :-D
Erster kleiner Versuch :freu2:
Liebe Grüße euer Tanto :p
Zur Zeit funktionieren +-*/ mit positiven Zahlen
Beispiel :-)
Eingabe =Range("D4")="6+4/2+1,1"
Ergebnis=Range("D5")=6,1
Quellcode
1. Option Explicit
Quellcode
1. Sub Rechner()
2. ReDim DatZahlen(0) As String
3. ReDim OpZahlen(0) As String
4. Dim DatZahlIndex As Integer
5. Dim AnzZahl As Integer
6. Dim OpZahlIndex As Integer
7. Dim Erg As Double
8. Dim Zzahl As Integer
9. AnzZahl = 1
10. Do
11. If SumZahlen(Cells(4, 4), AnzZahl) = "" Then Exit Do
12. DatZahlIndex = DatZahlIndex + 1
13. ReDim Preserve DatZahlen(DatZahlIndex)
14. DatZahlen(DatZahlIndex) = SumZahlen(Cells(4, 4), AnzZahl)
15. AnzZahl = AnzZahl + 1
16. Loop
17. AnzZahl = 1
18. Do
19. If SumOperatoren(Cells(4, 4), AnzZahl) = "" Then Exit Do
20. OpZahlIndex = OpZahlIndex + 1
21. ReDim Preserve OpZahlen(OpZahlIndex)
22. OpZahlen(OpZahlIndex) = SumOperatoren(Cells(4, 4), AnzZahl)
23. AnzZahl = AnzZahl + 1
24. Loop
25. Erg = CCur(DatZahlen(1))
26. For Zzahl = 1 To UBound(OpZahlen())
27. If OpZahlen(Zzahl) = "+" Then Erg = Erg + CCur(DatZahlen(Zzahl + 1))
28. If OpZahlen(Zzahl) = "-" Then Erg = Erg - CCur(DatZahlen(Zzahl + 1))
29. If OpZahlen(Zzahl) = "*" Then Erg = Erg * CCur(DatZahlen(Zzahl + 1))
30. If OpZahlen(Zzahl) = "/" Then Erg = Erg / CCur(DatZahlen(Zzahl + 1))
31. Cells(5, 4) = Erg
32. Next Zzahl
33. End Sub
Alles anzeigen
Quellcode
1. Function SumZahlen(Zellen As Variant, zaehler1 As Integer) As String
2. Dim Zelle As Range
3. Dim zeich1 As Integer
4. Dim schalter As Boolean
5. Dim zaehler3 As Integer
6. ReDim zaehler2(Len([Zellen])) As String
7. zaehler3 = 1
8. Application.Volatile
9. If zaehler1 > Len([Zellen]) Then zaehler1 = Len([Zellen])
10. For zeich1 = 1 To Len([Zellen])
11. If Mid([Zellen], zeich1, 1) Like "[0-9,.]" = True Then
12. zaehler2(zaehler3) = zaehler2(zaehler3) & Mid([Zellen], zeich1, 1)
13. schalter = True
14. End If
15. If schalter = True And Mid([Zellen], zeich1, 1) Like "[0-9,.]" = False Then
16. zaehler3 = zaehler3 + 1
17. schalter = False
18. End If
19. Next zeich1
20. SumZahlen = zaehler2(zaehler1)
21. End Function
Alles anzeigen
Quellcode
1. Function SumOperatoren(Zellen As Variant, zaehler1 As Integer) As String
2. Dim Zelle As Range
3. Dim zeich1 As Integer
4. Dim schalter As Boolean
5. Dim zaehler3 As Integer
6. ReDim zaehler2(Len([Zellen])) As String
7. zaehler3 = 1
8. Application.Volatile
9. If zaehler1 > Len([Zellen]) Then zaehler1 = Len([Zellen])
10. For zeich1 = 1 To Len([Zellen])
11. If Mid([Zellen], zeich1, 1) Like "[+-]" = True Or Mid([Zellen], zeich1, 1) = "*" Or Mid([Zellen], zeich1, 1) = "/" Then
12. zaehler2(zaehler3) = zaehler2(zaehler3) & Mid([Zellen], zeich1, 1)
13. schalter = True
14. End If
15. If schalter = True And Mid([Zellen], zeich1, 1) Like "[+-]" = False Or schalter = True And Mid([Zellen], zeich1, 1) <> "*" Or schalter = True And Mid([Zellen], zeich1, 1) <> "/" Then
16. zaehler3 = zaehler3 + 1
17. schalter = False
18. End If
19. Next zeich1
20. SumOperatoren = zaehler2(zaehler1)
21. End Function
Alles anzeigen
Dann war mir noch folgendes zur Like Syntax aufgefallen.
Diese beiden Zeichen wurden bemänngelt "*/",deshalb eine weitere oder verknüpfung in eine der obigen Functionen :evil:
Kurzbeschreibung wie zerlegt wird
Definierten String "6+4/2+1,1" bzw. eingabe
Zahlenblöcke werden einem Eindimensionalen Array übergeben,indexende mit Ubound ermittelt
6
4
2
1,1
Festgestellte Anzahl über Index =4 (der index ist der 2 Parameter der Functionen)
Operatoren werden isoliert
+
/
+
Festgestellte Anzahl über Index =3 (der index ist der 2 Parameter der Functionen)
Der erste Zahlenblock wird der Ergebnisvariablen zugewiesen
Nun können parallel Zahlenblöcke wie Operanden über If bedingungen die Ergebnisvariable füllen.
• Option Compare Database
Option Explicit
'Taschenrechner
Dim gmDezimal As Integer
Dim gmOperator As Double
Function Clear() '********************
'** Alles Löschen **
'********************
Dim f As Form
Set f = Forms!Taschenrechner
f!memoryfield = 0
f!Anzeige = 0
f!zeichen = ""
f!operator = 0
gmDezimal = 0
End Function
Function ziffern(z As Integer) '********************
'** Dezimalstellen **
Dim f As Form '********************
Set f = Forms!Taschenrechner
Dim g As Integer
If gmDezimal >= 1 Then
f!Anzeige = f!Anzeige + z / (10 ^ gmDezimal)
gmDezimal = gmDezimal + 1
Else
f!Anzeige = z + 10 * f!Anzeige
End If
End Function
Function rad() '*******************
'** Wurzelziehen **
'*******************
Dim x As Form
Set x = Forms!Taschenrechner
x!zeichen = "rad"
x!operator = x!operator & Sqr(x!Anzeige)
x!Anzeige = ""
End Function
Function rechnen(q As String)
Dim g As Integer
'********************
'** Rechnen **
'********************
Dim f As Form
Set f = Forms!Taschenrechner
gmDezimal = 0
If f!operator = 0 Or f!operator = "" Or f!operator = Null Then
f!operator = f!Anzeige & q
Else
f!operator = f!operator & f!Anzeige & q
End If
f!Anzeige = 0
End Function
Function result()
Dim f As Form
Dim str_Rechnen As String ' Länge der Zeichenfolge
Dim arr_Rechnen() As String 'Array
Dim len_Rechnen As Long 'Langzahlen
Dim operand As Boolean 'Zahl oder Rechenzeichen
Dim arr_Position As Integer 'Zahlen
Dim i As Integer 'Variable definieren
Dim msg As String
Dim o As Integer 'Variable definieren
Set f = Forms!Taschenrechner
f!operator = f!operator & f!Anzeige 'weiterführende Rechnung
str_Rechnen = f!operator 'Ganze Rechnung?
ReDim arr_Rechnen(len_Rechnen)
arr_Position = 0 'Anfang
For i = 1 To len_Rechnen
If i = 1 Or Mid(str_Rechnen, i, 1) = "," Then 'ertes Zeichen oder "," gehört immer zum operand deshalb operand immer True
operand = True
ElseIf operand = False Then 'Rechenzeichen
operand = True ' nach einem operator kommt immer ein operand
arr_Position = arr_Position + 1 'Ein Schritt weiter
Else
operand = IsNumeric(Mid(str_Rechnen, i, 1)) 'wird überprüft ob Zeichen Zahl ist
End If
If operand = True Then 'Dezimalzahl festlegen
If Mid(str_Rechnen, i, 1) = "," Then 'wenn ein komma getippt wird
arr_Rechnen(arr_Position) = arr_Rechnen(arr_Position) & "." 'Dann mit Punkt statt Komma rechnen
Else
arr_Rechnen(arr_Position) = arr_Rechnen(arr_Position) & Mid(str_Rechnen, i, 1) 'Wenn Zeichen eine Zahl dann ist sie dem gleichen Array angefügt
End If
Else 'ist ein operator Array wir um 1 erhöht und operator dem Array zugefügt
arr_Position = arr_Position + 1 'Ein Schritt weiter wenn kein Komma
arr_Rechnen(arr_Position) = Mid(str_Rechnen, i, 1)
End If
Next i
'Ausgabe zur Überprüfung des Arrays
For i = 0 To arr_Position
msg = msg & i & ": " & arr_Rechnen(i) & vbCrLf
Next i
Debug.Print (msg)
'*******
For i = 0 To arr_Position 'In dieser Schleife wird die Rechung gurchgeführt
If arr_Rechnen(i) = "*" Or arr_Rechnen(i) = "/" Then 'Wegen punkt vor strich muss zuerst * oder / gerechnet werden wenn das zutrifft, nimmt er den operand vor und nachdem operator und rechnet
'danach wird das Ergebnis auf die Position auf des ersten Operanten ins Array geschrieben
If arr_Rechnen(i) = "*" Then
o = i - 1
Do Until arr_Rechnen(o) <> "" 'Wenn Operant = "" dann ArrPosition zurück
o = o - 1
Loop
arr_Rechnen(o) = Str(Val(arr_Rechnen(o)) * Val(arr_Rechnen(i + 1)))
arr_Rechnen(i) = ""
arr_Rechnen(i + 1) = ""
Else
o = i - 1
Do Until arr_Rechnen(o) <> ""
o = o - 1
Loop
arr_Rechnen(o) = Str(Val(arr_Rechnen(o)) / Val(arr_Rechnen(i + 1)))
arr_Rechnen(i) = ""
arr_Rechnen(i + 1) = ""
End If
End If
Next i
For i = 0 To arr_Position
msg = msg & i & ": " & arr_Rechnen(i) & vbCrLf
Next i
Debug.Print (msg)
For i = 0 To arr_Position
If arr_Rechnen(i) = "+" Or arr_Rechnen(i) = "-" Then
If arr_Rechnen(i) = "+" Then
o = i - 1
Do Until arr_Rechnen(o) <> ""
o = o - 1
Loop
arr_Rechnen(o) = Str(Val(arr_Rechnen(o)) + Val(arr_Rechnen(i + 1)))
arr_Rechnen(i) = ""
arr_Rechnen(i + 1) = ""
Else
o = i - 1
Do Until arr_Rechnen(o) <> ""
o = o - 1
Loop
arr_Rechnen(o) = Str(Val(arr_Rechnen(o)) - Val(arr_Rechnen(i + 1)))
arr_Rechnen(i) = ""
arr_Rechnen(i + 1) = ""
End If
End If
Next i
For i = 0 To arr_Position
msg = msg & i & ": " & arr_Rechnen(i) & vbCrLf
Next i
Debug.Print (msg)
f!Anzeige = Val(arr_Rechnen(o))
'Case "*": f!Anzeige = f!Anzeige * f!operator
'f!operator = ""
'End Select
'f!operator = 0
End Function
Function plusminus()
'***********************
'** Vorzeichen ändern **
'***********************
Dim f As Form
Set f = Forms!Taschenrechner
f!Anzeige = f!Anzeige * (-1)
End Function
Function komma()
Debug.Print gmDezimal
If gmDezimal = 0 Then
gmDezimal = 1
End If
End Function
Function Back()
'*********************
'** Ziffern löschen **
'*********************
Dim f As Form
Set f = Forms!Taschenrechner
Debug.Print gmDezimal
If gmDezimal >= 2 Then
f!Anzeige = f!Anzeige * 10 ^ (gmDezimal - 2)
f!Anzeige = Int(f!Anzeige)
f!Anzeige = f!Anzeige / 10 ^ (gmDezimal - 2)
gmDezimal = gmDezimal - 1
Else
f!Anzeige = Int(f!Anzeige / 10)
gmDezimal = 0
End If
End Function
Function Taxplus() '********************
'** Plus Steuer **
'********************
Dim f As Form
Set f = Forms!Taschenrechner
f!Anzeige = f!Anzeige + f!Anzeige * (19 / 100)
End Function
Function Taxminus()
'********************
'** minus Steuer **
'********************
Dim f As Form
Set f = Forms!Taschenrechner
f!Anzeige = f!Anzeige - f!Anzeige * (19 / 100)
End Function
Function Memoryplus()
'****************************************
'** Addition des vorherigen Ergebnis **
'****************************************
Dim x As Form
Set x = Forms!Taschenrechner
x!memoryfield = x!operator
x!Anzeige = x!Anzeige + x!memoryfield
End Function
Function Memoryminus()
'*******************************************
'** Subtraktion des vorherigen Ergebnis **
'*******************************************
Dim x As Form
Set x = Forms!Taschenrechner
x!memoryfield = x!operator
x!Anzeige = x!Anzeige - x!memoryfield
End Function
Function memoryclear()
'****************************************
'** Löschen des vorherigen Ergebnis **
'****************************************
Dim x As Form
Set x = Forms!Taschenrechner
x!memoryfield = 0
End Function
Function etod()
'****************************************
'** Euro Dollar Wechsel **
'****************************************
Dim x As Form
Set x = Forms!Taschenrechner
x!operator = x!Anzeige * 1.336
End Function
Function dtoe()
'****************************************
'** Dollar Euro Wechsel **
'****************************************
Dim x As Form
Set x = Forms!Taschenrechner
x!operator = x!Anzeige / 1.336
End Function
Function hoch3()
'****************************************
'****** Potenz hoch 3 ******
'****************************************
Dim x As Form
Set x = Forms!Taschenrechner
x!zeichen = "^3"
x!operator = x!operator & x!Anzeige ^ 3
x!Anzeige = ""
End Function
Function hoch2()
'****************************************
'****** Potenz hoch 2 ******
'****************************************
Dim x As Form
Set x = Forms!Taschenrechner
x!zeichen = "^2"
x!operator = x!operator & x!Anzeige ^ 2
x!Anzeige = ""
End Function
Function hochx()
'****************************************
'****** Potenz hoch x ******
'****************************************
Dim x As Form
Set x = Forms!Taschenrechner
x!zeichen = "x^y"
x!operator = x!Anzeige
x!Anzeige = 0
End Function
|
{
"url": "https://www.paules-pc-forum.de/forum/thread/115920-taschenrechner-mit-visual-basic/?postID=993094&s=322fa585bcc8ee5226418d0a5c5443c86dd4ee5b",
"source_domain": "www.paules-pc-forum.de",
"snapshot_id": "crawl=CC-MAIN-2019-51",
"warc_metadata": {
"Content-Length": "208216",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:7PDJWDV5WWR5CWIBRJJYFL5LPDNAFHEZ",
"WARC-Concurrent-To": "<urn:uuid:fd4a6942-5338-4c82-b5e8-8310d5424f5a>",
"WARC-Date": "2019-12-08T00:10:29Z",
"WARC-IP-Address": "217.160.0.57",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:W354GL2KSHLH3OJV4XKP2ZB4TMTSZ4MA",
"WARC-Record-ID": "<urn:uuid:d44d4d4e-d558-445f-bf1b-dbfedec48c3f>",
"WARC-Target-URI": "https://www.paules-pc-forum.de/forum/thread/115920-taschenrechner-mit-visual-basic/?postID=993094&s=322fa585bcc8ee5226418d0a5c5443c86dd4ee5b",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:59b28214-3520-4c6e-8132-b4fe035c332a>"
},
"warc_info": "isPartOf: CC-MAIN-2019-51\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for December 2019\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-207.ec2.internal\r\nsoftware: Apache Nutch 1.16 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.1-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
32,
33,
186,
187,
373,
374,
412,
413,
630,
1012,
1064,
1065,
1105,
1183,
1184,
1233,
1280,
1281,
1295,
1296,
1349,
1350,
1364,
1365,
1409,
1410,
1424,
1425,
1472,
1473,
1487,
1488,
1533,
1534,
1548,
1549,
1589,
1614,
1628,
1629,
1669,
1694,
1708,
1709,
1749,
1774,
1788,
1789,
1829,
1854,
1868,
1869,
1909,
1934,
1948,
1949,
1989,
2014,
2028,
2029,
2069,
2094,
2108,
2109,
2149,
2174,
2188,
2189,
2229,
2254,
2268,
2269,
2309,
2334,
2348,
2349,
2392,
2393,
2407,
2408,
2440,
2472,
2495,
2496,
2609,
2610,
2791,
2792,
2859,
2860,
2935,
3007,
3081,
3156,
3187,
3212,
3226,
3292,
3323,
3348,
3362,
3428,
3459,
3484,
3498,
3564,
3595,
3620,
3634,
3700,
3731,
3756,
3770,
3836,
3867,
3892,
3906,
3972,
4003,
4028,
4042,
4108,
4139,
4164,
4178,
4244,
4275,
4300,
4314,
4380,
4416,
4445,
4460,
4512,
4529,
4543,
4609,
4643,
4680,
4703,
4727,
4741,
4742,
4743,
4796,
4797,
4808,
4821,
4948,
4979,
4980,
5018,
5019,
5191,
5192,
5348,
5349,
5435,
5436,
5468,
5469,
5684,
5685,
5701,
5702,
5724,
5762,
5796,
5859,
5904,
5972,
6009,
6025,
6047,
6093,
6121,
6186,
6228,
6277,
6342,
6359,
6390,
6456,
6494,
6537,
6596,
6613,
6636,
6683,
6746,
6767,
6785,
6806,
6807,
6823,
6824,
6844,
6885,
6902,
6903,
6919,
6920,
6941,
6982,
6999,
7000,
7016,
7017,
7036,
7077,
7094,
7095,
7111,
7112,
7135,
7176,
7193,
7194,
7195,
7231,
7232,
7295,
7296,
7369,
7370,
7458,
7459,
7519,
7520,
7559,
7745,
7777,
7778,
7794,
7795,
7829,
7863,
7892,
7936,
7970,
8009,
8046,
8062,
8079,
8124,
8164,
8202,
8220,
8265,
8305,
8343,
8361,
8406,
8446,
8484,
8502,
8547,
8587,
8625,
8643,
8688,
8728,
8766,
8784,
8829,
8869,
8907,
8925,
8970,
9010,
9048,
9066,
9111,
9151,
9189,
9207,
9252,
9292,
9330,
9348,
9419,
9445,
9471,
9495,
9525,
9547,
9565,
9614,
9654,
9692,
9710,
9758,
9792,
9819,
9845,
9863,
9908,
9941,
9974,
9993,
10038,
10070,
10106,
10127,
10145,
10166,
10183,
10184,
10262,
10302,
10303,
10379,
10440,
10441,
10528,
10529,
10542,
10555,
10682,
10714,
10715,
10769,
10770,
10845,
10846,
10908,
10909,
10941,
10942,
10958,
10959,
10990,
11028,
11060,
11081,
11093,
11168,
11222,
11239,
11253,
11295,
11344,
11412,
11444,
11461,
11476,
11523,
11632,
11689,
11710,
11728,
11749,
11750,
11766,
11767,
11845,
11873,
11904,
11937,
11970,
12019,
12041,
12071,
12138,
12180,
12245,
12322,
12348,
12365,
12451,
12485,
12512,
12529,
12551,
12592,
12615,
12636,
12637,
12638,
12719,
12720,
12735,
12756,
12768,
12816,
12848,
12849,
12886,
12887,
12919,
12920,
12975,
12976,
12995,
12996,
13035,
13066,
13067,
13083,
13084,
13109,
13110,
13126,
13127,
13150,
13188,
13225,
13262,
13294,
13330,
13357,
13387,
13408,
13421,
13484,
13526,
13575,
13643,
13675,
13690,
13712,
13725,
13792,
13832,
13879,
13949,
13981,
13996,
14031,
14077,
14156,
14235,
14314,
14393,
14421,
14442,
14460,
14481,
14482,
14498,
14499,
14577,
14605,
14636,
14669,
14702,
14751,
14773,
14803,
14870,
14912,
14977,
15054,
15080,
15097,
15183,
15217,
15244,
15261,
15283,
15324,
15347,
15368,
15369,
15385,
15386,
15468,
15496,
15527,
15560,
15593,
15642,
15664,
15694,
15761,
15803,
15933,
16010,
16036,
16053,
16246,
16280,
16307,
16324,
16346,
16391,
16414,
16435,
16436,
16437,
16500,
16625,
16626,
16666,
16667,
16717,
16718,
16814,
16822,
16830,
16838,
16848,
16936,
16937,
16970,
16978,
16986,
16994,
17082,
17083,
17149,
17150,
17252,
17282,
17304,
17326,
17357,
17388,
17389,
17390,
17391,
17392,
17437,
17464,
17492,
17493,
17494,
17514,
17515,
17550,
17551,
17575,
17595,
17616,
17637,
17657,
17658,
17677,
17678,
17737,
17765,
17807,
17808,
17843,
17866,
17867,
17868,
17869,
17898,
17949,
17950,
17982,
17983,
17994,
18031,
18044,
18045,
18046,
18047,
18048,
18049,
18050,
18051,
18070,
18071,
18072,
18114,
18140,
18167,
18168,
18188,
18189,
18224,
18225,
18226,
18250,
18251,
18298,
18299,
18320,
18321,
18340,
18341,
18342,
18378,
18401,
18402,
18403,
18431,
18452,
18480,
18481,
18501,
18536,
18537,
18557,
18626,
18659,
18670,
18716,
18729,
18749,
18750,
18751,
18752,
18753,
18772,
18773,
18774,
18775,
18776,
18777,
18778,
18779,
18803,
18804,
18824,
18825,
18882,
18923,
18965,
19019,
19061,
19105,
19129,
19173,
19174,
19209,
19276,
19324,
19361,
19362,
19393,
19424,
19552,
19573,
19622,
19689,
19747,
19758,
19844,
19857,
19858,
19910,
19982,
20084,
20095,
20245,
20258,
20341,
20415,
20472,
20485,
20498,
20540,
20572,
20625,
20638,
20662,
20677,
20759,
20957,
21053,
21088,
21104,
21183,
21199,
21210,
21284,
21310,
21340,
21351,
21367,
21403,
21419,
21430,
21504,
21530,
21560,
21573,
21586,
21599,
21631,
21684,
21697,
21721,
21753,
21812,
21847,
21863,
21899,
21915,
21926,
22000,
22026,
22056,
22067,
22083,
22119,
22135,
22146,
22220,
22246,
22276,
22289,
22302,
22315,
22347,
22400,
22413,
22437,
22438,
22476,
22477,
22478,
22479,
22531,
22532,
22555,
22556,
22574,
22596,
22597,
22598,
22599,
22600,
22601,
22602,
22603,
22622,
22623,
22624,
22651,
22682,
22713,
22744,
22745,
22765,
22766,
22801,
22802,
22837,
22838,
22857,
22858,
22859,
22860,
22861,
22884,
22885,
22886,
22887,
22915,
22916,
22917,
22945,
22946,
22966,
22967,
22980,
22981,
22982,
23001,
23002,
23003,
23025,
23054,
23083,
23112,
23113,
23114,
23134,
23135,
23170,
23171,
23172,
23200,
23201,
23202,
23203,
23204,
23205,
23234,
23235,
23236,
23237,
23238,
23289,
23322,
23373,
23374,
23406,
23407,
23408,
23409,
23420,
23421,
23459,
23460,
23480,
23481,
23482,
23483,
23496,
23497,
23498,
23517,
23518,
23519,
23520,
23521,
23568,
23593,
23621,
23622,
23623,
23624,
23644,
23645,
23680,
23681,
23734,
23735,
23736,
23737,
23756,
23757,
23758,
23759,
23760,
23761,
23762,
23763,
23789,
23817,
23843,
23871,
23872,
23873,
23893,
23894,
23929,
23930,
23983,
23984,
23985,
24004,
24005,
24006,
24007,
24008,
24009,
24037,
24085,
24131,
24179,
24180,
24181,
24201,
24202,
24237,
24238,
24239,
24272,
24273,
24317,
24318,
24319,
24320,
24321,
24340,
24341,
24342,
24343,
24344,
24345,
24346,
24347,
24376,
24377,
24428,
24477,
24528,
24529,
24530,
24550,
24551,
24586,
24587,
24588,
24621,
24622,
24666,
24667,
24668,
24669,
24670,
24689,
24690,
24691,
24692,
24721,
24769,
24814,
24862,
24863,
24864,
24865,
24885,
24886,
24921,
24922,
24923,
24947,
24948,
24949,
24950,
24951,
24952,
24953,
24972,
24973,
24974,
24975,
24997,
25045,
25078,
25126,
25127,
25128,
25148,
25183,
25184,
25185,
25186,
25223,
25224,
25225,
25244,
25245,
25246,
25268,
25269,
25317,
25350,
25398,
25399,
25419,
25454,
25455,
25492,
25493,
25512,
25513,
25514,
25515,
25516,
25517,
25518,
25519,
25520,
25543,
25544,
25592,
25627,
25675,
25676,
25696,
25697,
25732,
25733,
25734,
25735,
25758,
25759,
25805,
25826,
25827,
25828,
25847,
25848,
25849,
25872,
25873,
25921,
25956,
26004,
26005,
26006,
26007,
26027,
26028,
26063,
26064,
26065,
26066,
26089,
26090,
26136,
26157,
26158,
26177,
26178,
26179,
26202,
26203,
26251,
26286,
26334,
26335,
26355,
26356,
26391,
26415,
26444,
26445,
26465,
26466,
26467,
26468
],
"line_end_idx": [
32,
33,
186,
187,
373,
374,
412,
413,
630,
1012,
1064,
1065,
1105,
1183,
1184,
1233,
1280,
1281,
1295,
1296,
1349,
1350,
1364,
1365,
1409,
1410,
1424,
1425,
1472,
1473,
1487,
1488,
1533,
1534,
1548,
1549,
1589,
1614,
1628,
1629,
1669,
1694,
1708,
1709,
1749,
1774,
1788,
1789,
1829,
1854,
1868,
1869,
1909,
1934,
1948,
1949,
1989,
2014,
2028,
2029,
2069,
2094,
2108,
2109,
2149,
2174,
2188,
2189,
2229,
2254,
2268,
2269,
2309,
2334,
2348,
2349,
2392,
2393,
2407,
2408,
2440,
2472,
2495,
2496,
2609,
2610,
2791,
2792,
2859,
2860,
2935,
3007,
3081,
3156,
3187,
3212,
3226,
3292,
3323,
3348,
3362,
3428,
3459,
3484,
3498,
3564,
3595,
3620,
3634,
3700,
3731,
3756,
3770,
3836,
3867,
3892,
3906,
3972,
4003,
4028,
4042,
4108,
4139,
4164,
4178,
4244,
4275,
4300,
4314,
4380,
4416,
4445,
4460,
4512,
4529,
4543,
4609,
4643,
4680,
4703,
4727,
4741,
4742,
4743,
4796,
4797,
4808,
4821,
4948,
4979,
4980,
5018,
5019,
5191,
5192,
5348,
5349,
5435,
5436,
5468,
5469,
5684,
5685,
5701,
5702,
5724,
5762,
5796,
5859,
5904,
5972,
6009,
6025,
6047,
6093,
6121,
6186,
6228,
6277,
6342,
6359,
6390,
6456,
6494,
6537,
6596,
6613,
6636,
6683,
6746,
6767,
6785,
6806,
6807,
6823,
6824,
6844,
6885,
6902,
6903,
6919,
6920,
6941,
6982,
6999,
7000,
7016,
7017,
7036,
7077,
7094,
7095,
7111,
7112,
7135,
7176,
7193,
7194,
7195,
7231,
7232,
7295,
7296,
7369,
7370,
7458,
7459,
7519,
7520,
7559,
7745,
7777,
7778,
7794,
7795,
7829,
7863,
7892,
7936,
7970,
8009,
8046,
8062,
8079,
8124,
8164,
8202,
8220,
8265,
8305,
8343,
8361,
8406,
8446,
8484,
8502,
8547,
8587,
8625,
8643,
8688,
8728,
8766,
8784,
8829,
8869,
8907,
8925,
8970,
9010,
9048,
9066,
9111,
9151,
9189,
9207,
9252,
9292,
9330,
9348,
9419,
9445,
9471,
9495,
9525,
9547,
9565,
9614,
9654,
9692,
9710,
9758,
9792,
9819,
9845,
9863,
9908,
9941,
9974,
9993,
10038,
10070,
10106,
10127,
10145,
10166,
10183,
10184,
10262,
10302,
10303,
10379,
10440,
10441,
10528,
10529,
10542,
10555,
10682,
10714,
10715,
10769,
10770,
10845,
10846,
10908,
10909,
10941,
10942,
10958,
10959,
10990,
11028,
11060,
11081,
11093,
11168,
11222,
11239,
11253,
11295,
11344,
11412,
11444,
11461,
11476,
11523,
11632,
11689,
11710,
11728,
11749,
11750,
11766,
11767,
11845,
11873,
11904,
11937,
11970,
12019,
12041,
12071,
12138,
12180,
12245,
12322,
12348,
12365,
12451,
12485,
12512,
12529,
12551,
12592,
12615,
12636,
12637,
12638,
12719,
12720,
12735,
12756,
12768,
12816,
12848,
12849,
12886,
12887,
12919,
12920,
12975,
12976,
12995,
12996,
13035,
13066,
13067,
13083,
13084,
13109,
13110,
13126,
13127,
13150,
13188,
13225,
13262,
13294,
13330,
13357,
13387,
13408,
13421,
13484,
13526,
13575,
13643,
13675,
13690,
13712,
13725,
13792,
13832,
13879,
13949,
13981,
13996,
14031,
14077,
14156,
14235,
14314,
14393,
14421,
14442,
14460,
14481,
14482,
14498,
14499,
14577,
14605,
14636,
14669,
14702,
14751,
14773,
14803,
14870,
14912,
14977,
15054,
15080,
15097,
15183,
15217,
15244,
15261,
15283,
15324,
15347,
15368,
15369,
15385,
15386,
15468,
15496,
15527,
15560,
15593,
15642,
15664,
15694,
15761,
15803,
15933,
16010,
16036,
16053,
16246,
16280,
16307,
16324,
16346,
16391,
16414,
16435,
16436,
16437,
16500,
16625,
16626,
16666,
16667,
16717,
16718,
16814,
16822,
16830,
16838,
16848,
16936,
16937,
16970,
16978,
16986,
16994,
17082,
17083,
17149,
17150,
17252,
17282,
17304,
17326,
17357,
17388,
17389,
17390,
17391,
17392,
17437,
17464,
17492,
17493,
17494,
17514,
17515,
17550,
17551,
17575,
17595,
17616,
17637,
17657,
17658,
17677,
17678,
17737,
17765,
17807,
17808,
17843,
17866,
17867,
17868,
17869,
17898,
17949,
17950,
17982,
17983,
17994,
18031,
18044,
18045,
18046,
18047,
18048,
18049,
18050,
18051,
18070,
18071,
18072,
18114,
18140,
18167,
18168,
18188,
18189,
18224,
18225,
18226,
18250,
18251,
18298,
18299,
18320,
18321,
18340,
18341,
18342,
18378,
18401,
18402,
18403,
18431,
18452,
18480,
18481,
18501,
18536,
18537,
18557,
18626,
18659,
18670,
18716,
18729,
18749,
18750,
18751,
18752,
18753,
18772,
18773,
18774,
18775,
18776,
18777,
18778,
18779,
18803,
18804,
18824,
18825,
18882,
18923,
18965,
19019,
19061,
19105,
19129,
19173,
19174,
19209,
19276,
19324,
19361,
19362,
19393,
19424,
19552,
19573,
19622,
19689,
19747,
19758,
19844,
19857,
19858,
19910,
19982,
20084,
20095,
20245,
20258,
20341,
20415,
20472,
20485,
20498,
20540,
20572,
20625,
20638,
20662,
20677,
20759,
20957,
21053,
21088,
21104,
21183,
21199,
21210,
21284,
21310,
21340,
21351,
21367,
21403,
21419,
21430,
21504,
21530,
21560,
21573,
21586,
21599,
21631,
21684,
21697,
21721,
21753,
21812,
21847,
21863,
21899,
21915,
21926,
22000,
22026,
22056,
22067,
22083,
22119,
22135,
22146,
22220,
22246,
22276,
22289,
22302,
22315,
22347,
22400,
22413,
22437,
22438,
22476,
22477,
22478,
22479,
22531,
22532,
22555,
22556,
22574,
22596,
22597,
22598,
22599,
22600,
22601,
22602,
22603,
22622,
22623,
22624,
22651,
22682,
22713,
22744,
22745,
22765,
22766,
22801,
22802,
22837,
22838,
22857,
22858,
22859,
22860,
22861,
22884,
22885,
22886,
22887,
22915,
22916,
22917,
22945,
22946,
22966,
22967,
22980,
22981,
22982,
23001,
23002,
23003,
23025,
23054,
23083,
23112,
23113,
23114,
23134,
23135,
23170,
23171,
23172,
23200,
23201,
23202,
23203,
23204,
23205,
23234,
23235,
23236,
23237,
23238,
23289,
23322,
23373,
23374,
23406,
23407,
23408,
23409,
23420,
23421,
23459,
23460,
23480,
23481,
23482,
23483,
23496,
23497,
23498,
23517,
23518,
23519,
23520,
23521,
23568,
23593,
23621,
23622,
23623,
23624,
23644,
23645,
23680,
23681,
23734,
23735,
23736,
23737,
23756,
23757,
23758,
23759,
23760,
23761,
23762,
23763,
23789,
23817,
23843,
23871,
23872,
23873,
23893,
23894,
23929,
23930,
23983,
23984,
23985,
24004,
24005,
24006,
24007,
24008,
24009,
24037,
24085,
24131,
24179,
24180,
24181,
24201,
24202,
24237,
24238,
24239,
24272,
24273,
24317,
24318,
24319,
24320,
24321,
24340,
24341,
24342,
24343,
24344,
24345,
24346,
24347,
24376,
24377,
24428,
24477,
24528,
24529,
24530,
24550,
24551,
24586,
24587,
24588,
24621,
24622,
24666,
24667,
24668,
24669,
24670,
24689,
24690,
24691,
24692,
24721,
24769,
24814,
24862,
24863,
24864,
24865,
24885,
24886,
24921,
24922,
24923,
24947,
24948,
24949,
24950,
24951,
24952,
24953,
24972,
24973,
24974,
24975,
24997,
25045,
25078,
25126,
25127,
25128,
25148,
25183,
25184,
25185,
25186,
25223,
25224,
25225,
25244,
25245,
25246,
25268,
25269,
25317,
25350,
25398,
25399,
25419,
25454,
25455,
25492,
25493,
25512,
25513,
25514,
25515,
25516,
25517,
25518,
25519,
25520,
25543,
25544,
25592,
25627,
25675,
25676,
25696,
25697,
25732,
25733,
25734,
25735,
25758,
25759,
25805,
25826,
25827,
25828,
25847,
25848,
25849,
25872,
25873,
25921,
25956,
26004,
26005,
26006,
26007,
26027,
26028,
26063,
26064,
26065,
26066,
26089,
26090,
26136,
26157,
26158,
26177,
26178,
26179,
26202,
26203,
26251,
26286,
26334,
26335,
26355,
26356,
26391,
26415,
26444,
26445,
26465,
26466,
26467,
26468,
26486
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 26486,
"ccnet_original_nlines": 1020,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.0449322909116745,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.0024620399344712496,
"rps_doc_frac_lines_end_with_ellipsis": 0.000979430042207241,
"rps_doc_frac_no_alph_words": 0.4509643018245697,
"rps_doc_frac_unique_words": 0.2472429722547531,
"rps_doc_mean_word_length": 5.291711330413818,
"rps_doc_num_sentences": 415,
"rps_doc_symbol_to_word_ratio": 0.0002051699993899092,
"rps_doc_unigram_entropy": 5.656308650970459,
"rps_doc_word_count": 2811,
"rps_doc_frac_chars_dupe_10grams": 0.2118319272994995,
"rps_doc_frac_chars_dupe_5grams": 0.34857141971588135,
"rps_doc_frac_chars_dupe_6grams": 0.2875294089317322,
"rps_doc_frac_chars_dupe_7grams": 0.27112606167793274,
"rps_doc_frac_chars_dupe_8grams": 0.2463865429162979,
"rps_doc_frac_chars_dupe_9grams": 0.2233949601650238,
"rps_doc_frac_chars_top_2gram": 0.019361339509487152,
"rps_doc_frac_chars_top_3gram": 0.021848740056157112,
"rps_doc_frac_chars_top_4gram": 0.02689076028764248,
"rps_doc_books_importance": -2156.970458984375,
"rps_doc_books_importance_length_correction": -2156.970458984375,
"rps_doc_openwebtext_importance": -1041.4656982421875,
"rps_doc_openwebtext_importance_length_correction": -1041.4656982421875,
"rps_doc_wikipedia_importance": -986.110595703125,
"rps_doc_wikipedia_importance_length_correction": -986.110595703125
},
"fasttext": {
"dclm": 0.9059872627258301,
"english": 0.054744891822338104,
"fineweb_edu_approx": 3.0125625133514404,
"eai_general_math": 0.359325110912323,
"eai_open_web_math": 0.6423301696777344,
"eai_web_code": 0.4114565849304199
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.133",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "4",
"label": "Analyze"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "4",
"label": "Code/Software"
}
},
"extraction_artifacts": {
"primary": {
"code": "3",
"label": "Irrelevant Content"
},
"secondary": {
"code": "0",
"label": "No Artifacts"
}
},
"missing_content": {
"primary": {
"code": "4",
"label": "Missing Images or Figures"
},
"secondary": {
"code": "0",
"label": "No missing content"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "23",
"label": "Tutorial"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "2",
"label": "Partially Correct"
}
},
"education_level": {
"primary": {
"code": "3",
"label": "Undergraduate Level"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
7,248,943,462,311,270,000
|
7
\$\begingroup\$
In the past few days, I saw 2 questions that were asking for a review of code written for a programming challenge.
However, both of them had something strange, I hadn't seen in other questions. The OP was asking for a review of his solution, which was written in two languages. Specifically this question.
Personally, I see this as two questions, because both of the languages are different and hence the reviews would be completely different. Nevertheless, it has been framed into a single question.
Is this allowed?
I'm currently learning c++ coming from a python background, so I'll include a solution in python and in c++ for the following problem statement and based on very helpful answers obtained on my previous question I made some improvements in the c++ implementation:
If this isn't allowed, how should I report this to moderators?
link to the first question
link to the second question
I strongly believe that it should be formatted into two questions. Otherwise, I feel that the question wouldn't be focused + it's likely that the reviewer doesn't know both the languages, in that case, he would only be able to review a part of the question.
To re-enforce a point made by @Reinderien, accepting only one answer won't make sense in these kinds of questions too.
\$\endgroup\$
• 4
\$\begingroup\$ For the record: if it's not allowed, it should be flagged for closure, not for moderator attention. The higher-reputation users of the community can sort this out, it's not necessary to involve a moderator. \$\endgroup\$ – Mast Nov 2 '20 at 14:50
• 2
\$\begingroup\$ Do you have a cause/motivation based on the help center to disallow it? \$\endgroup\$ – Mast Nov 2 '20 at 14:52
• 3
\$\begingroup\$ If the comparative-review tag is there, it is perfectly ok. You can also add the comparative-review tag. That particular question is interested in performance in both languages so it I don't think it is a problem. \$\endgroup\$ – pacmaninbw Nov 2 '20 at 14:56
• \$\begingroup\$ @Mast am I allowed to give my personal opinion on meta? I wanted to see what others thought of it \$\endgroup\$ – Aryan Parekh Nov 2 '20 at 15:50
• 1
\$\begingroup\$ That does not address my points. \$\endgroup\$ – Mast Nov 2 '20 at 17:41
• 1
\$\begingroup\$ The duplicate target is not the same question. That question: "Can someone post the same problem in multiple questions?" This question: "Can someone post multiple solutions in the same question?" \$\endgroup\$ – mdfst13 Nov 4 '20 at 14:25
• 1
\$\begingroup\$ @mdfst13 I have voted to re-open \$\endgroup\$ – Aryan Parekh Nov 4 '20 at 15:05
7
\$\begingroup\$
I don't know the policy well enough to say whether it explicitly prohibits this, but my opinion is:
If the fundamental question is solid enough, then I wouldn't recommend closure - we already have a large-enough closure rate, and I wouldn't advocate yet one more reason to push well-meaning users away. Instead, I would offer the advice to the OP that there are many pockets of specialization on CR, and they will get higher attention and higher-quality answers from a question that is tagged to only one language; so the question should be split.
The StackExchange incentive structure is such that "the best" answer should be accepted, but where there are multiple languages at play, "the best" answer is IMO fairly apples-and-oranges. It makes less sense to only accept one answer that is (potentially) language-specific than it does to accept an answer for each language, and the only way that's possible is multiple questions.
Said another way, I don't trust that it's feasible to ask for a meaningful, comprehensive answer on every language submitted in one question. It's a lot to ask of a reviewer to give good advice to an arbitrarily broad range of technologies at once, and this would push out intermediate programmers whose technological breadth may be somewhat small but could - on a single-language question - provide perfectly fine advice.
\$\endgroup\$
7
\$\begingroup\$
On-topic, discouraged
Posting solutions to the same programming challenge in multiple languages in one question is discouraged. Posting multiple solutions is not off-topic, whether it be in one or more posts. As such the discouragement is unlikely to be accompanied by a slap on the wrist - closure, downvotes, comments.
Note: It is encouraged to leave some time before posting similar questions.
• I would ask two separate questions because (as you said) they are totally independent and smaller questions are easier to answer. (You can link them, of course.)
If there is a chance that they are not totally independent I'd consider asking the first question and waiting for a few days or reviews before posting the second one. You might get feedbacks which requires some modification in the code of the second question.
palacsint, CC BY-SA 3.0
• Please go ahead and post three questions, one for each language, and feel free to have them link to each other.
You may also want to consider to post your questions a bit apart, as answers to one of the languages might improve the code for another language.
Simon Forsberg, CC BY-SA 3.0
\$\endgroup\$
4
\$\begingroup\$
While there currently appears to be nothing in the rules against this practice, I would recommend making separate posts. Some reviewers may only be familiar one language though others may be familiar with multiple. The biggest advantage I see to separate posts is that there is a potential for more reputation and badges, which opens the door to more privileges on the site.
\$\endgroup\$
You must log in to answer this question.
Not the answer you're looking for? Browse other questions tagged .
|
{
"url": "https://codereview.meta.stackexchange.com/questions/10574/are-you-allowed-to-ask-for-reviews-of-the-same-program-written-in-two-languages/10575",
"source_domain": "codereview.meta.stackexchange.com",
"snapshot_id": "crawl=CC-MAIN-2021-04",
"warc_metadata": {
"Content-Length": "151174",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:FLTV7F6IQCIE2YBFOVO27CKIIULGQCWD",
"WARC-Concurrent-To": "<urn:uuid:028020af-9813-4a18-99d6-a6b27123c31e>",
"WARC-Date": "2021-01-23T11:13:36Z",
"WARC-IP-Address": "151.101.1.69",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:T5F5KJ7DFM3ICZVGS5X6KMXQ2N7OIM5I",
"WARC-Record-ID": "<urn:uuid:b548c1aa-3227-4521-8e1f-017b292ce12b>",
"WARC-Target-URI": "https://codereview.meta.stackexchange.com/questions/10574/are-you-allowed-to-ask-for-reviews-of-the-same-program-written-in-two-languages/10575",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:20e48bf5-4ef3-4d5f-8409-5e49e102b7a4>"
},
"warc_info": "isPartOf: CC-MAIN-2021-04\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for January 2021\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-254.ec2.internal\r\nsoftware: Apache Nutch 1.17 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.2-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: http://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
2,
18,
19,
134,
135,
326,
327,
522,
523,
540,
541,
804,
805,
868,
869,
896,
924,
925,
1183,
1184,
1303,
1304,
1318,
1324,
1591,
1597,
1729,
1735,
2015,
2181,
2187,
2280,
2286,
2545,
2551,
2652,
2654,
2670,
2671,
2771,
2772,
3220,
3221,
3604,
3605,
4028,
4029,
4043,
4045,
4061,
4062,
4084,
4085,
4384,
4460,
4461,
4627,
4628,
4892,
4893,
4921,
4922,
5038,
5039,
5189,
5190,
5223,
5224,
5238,
5240,
5256,
5257,
5632,
5633,
5647,
5648,
5689,
5690
],
"line_end_idx": [
2,
18,
19,
134,
135,
326,
327,
522,
523,
540,
541,
804,
805,
868,
869,
896,
924,
925,
1183,
1184,
1303,
1304,
1318,
1324,
1591,
1597,
1729,
1735,
2015,
2181,
2187,
2280,
2286,
2545,
2551,
2652,
2654,
2670,
2671,
2771,
2772,
3220,
3221,
3604,
3605,
4028,
4029,
4043,
4045,
4061,
4062,
4084,
4085,
4384,
4460,
4461,
4627,
4628,
4892,
4893,
4921,
4922,
5038,
5039,
5189,
5190,
5223,
5224,
5238,
5240,
5256,
5257,
5632,
5633,
5647,
5648,
5689,
5690,
5756
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 5756,
"ccnet_original_nlines": 78,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.41680532693862915,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.02662229910492897,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.22379368543624878,
"rps_doc_frac_unique_words": 0.38583511114120483,
"rps_doc_mean_word_length": 4.690274715423584,
"rps_doc_num_sentences": 46,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 5.2919769287109375,
"rps_doc_word_count": 946,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0.03267974033951759,
"rps_doc_frac_chars_dupe_6grams": 0.014198780059814453,
"rps_doc_frac_chars_dupe_7grams": 0.014198780059814453,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.014198780059814453,
"rps_doc_frac_chars_top_3gram": 0.006761330179870129,
"rps_doc_frac_chars_top_4gram": 0.009015100076794624,
"rps_doc_books_importance": -458.5791320800781,
"rps_doc_books_importance_length_correction": -458.5791320800781,
"rps_doc_openwebtext_importance": -281.6148681640625,
"rps_doc_openwebtext_importance_length_correction": -281.6148681640625,
"rps_doc_wikipedia_importance": -211.1514892578125,
"rps_doc_wikipedia_importance_length_correction": -211.1514892578125
},
"fasttext": {
"dclm": 0.34937840700149536,
"english": 0.9539844989776611,
"fineweb_edu_approx": 1.3454320430755615,
"eai_general_math": 0.936755895614624,
"eai_open_web_math": 0.2736359238624573,
"eai_web_code": 0.47435081005096436
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.1",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "302.22",
"labels": {
"level_1": "Social sciences",
"level_2": "",
"level_3": "Social psychology"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "5",
"label": "Evaluate"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "2",
"label": "Conceptual"
},
"secondary": {
"code": "3",
"label": "Procedural"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"extraction_artifacts": {
"primary": {
"code": "1",
"label": "Leftover HTML"
},
"secondary": {
"code": "3",
"label": "Irrelevant Content"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "8",
"label": "Documentation"
}
},
"reasoning_depth": {
"primary": {
"code": "3",
"label": "Intermediate Reasoning"
},
"secondary": {
"code": "2",
"label": "Basic Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "6",
"label": "Not Applicable/Indeterminate"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "1",
"label": "General Audience"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|
3,710,910,394,172,482,600
|
images stored sideways
Been using Scrivener for a couple of months now and moved lots of writing to it - thanks, it’s great.
My question is:
I dragged a picture folder into the research section. If I look at this folder in Preview they are all the right orientation. But Scrivener has them all on end/sideways (however you describe it!). I can’t find a control to turn them. I’m probably missing something obvious but I do need them the right way round. Can anyone help, please? Thanks.
Double-click on the image and you’ll get some controls, including a rotation tool.
Thanks, Amber - knew it would be obvious! I’ve clicked on each separately and turned them.
But - this doesn’t turn them on the corkboard. They’re still on end. I’d like them ok here too - it’s nice to see them all together, as they’re the setting for the story. Any way to do this? (It seems bizarre they are not the normal way round anyway!)
Images are pulled into Scrivener in the way they are stored on file. Preview may display them differently depending on your settings in Preview, but if you opened them in another editor - such as PhotoShop - you would see that they are the same way as in Scrivener. The key is to set up the rotation before importing into Scrivener (the rotation controls in Scrivener only affect how the image is viewed and do not affect the underlying file).
All the best,
Keith
Thanks, Keith. I’ll open the folder elsewhere and see what happens. Cheers!
Unfortunately, I just checked the original folder out in photoshop, opening the pix one at a time, and they all display the correct way round. So I can’t change them as they don’t need it. Oh well, it’s a small point and you have given me enough time already! I’ll just manage with the corkboard images sideways, so to speak. Thanks.
Can you send me one of the images? To support AT literatureandlatte DOT com? This is very strange as Scrivener doesn’t do any rotation to the file, so this shouldn’t (in theory) be happening, so if you can send me an affected file I would like to see what is causing it.
Thanks!
All the best,
Keith
Okay - done. I’ve just sent one.
Thanks.
I could be wrong but this sounds like it’s to do with the EXIF metadata in the jpeg. Preview and some other apps read the EXIF and perform a rotation, and even allow you to save the file with the new rotation.
BUT! they’ve only edited the EXIF data (in order to preserve detail and prevent degradation of the jpeg from resampling) which means when you open the image in, say, a web browser (which doesn’t read the EXIF data) your image is in the original un-rotated format.
Robin
Thanks, Robin, that sounds exactly what it was. EMP sent me the file and it did indeed open right-way-up in Photoshop and Preview, but in web browsers and Mail it was rotated. Re-saving in Photoshop caused it to open fine everywhere. EMP tells me that she took these photos on a phone camera, so that may be the reason behind the rotated EXIF data. Thanks for the explanation, as I know very little about how .jpeg data works myself, so you seem to have hit the nail on the head!
All the best,
Keith
I agree, that seems to have been the problem and I will add that info to my store of ‘sort-of-knowledge’, Robin. Thanks to you and to Keith. Now to go to PS and re-save all the photos!
Eleanor
|
{
"url": "https://forum.literatureandlatte.com/t/images-stored-sideways/5794",
"source_domain": "forum.literatureandlatte.com",
"snapshot_id": "CC-MAIN-2023-50",
"warc_metadata": {
"Content-Length": "35063",
"Content-Type": "application/http; msgtype=response",
"WARC-Block-Digest": "sha1:ZULHISU5QSNLMTPXEYOEHMBEHXRNGAP7",
"WARC-Concurrent-To": "<urn:uuid:b5097e64-a04b-456c-9b16-a65c361fb06a>",
"WARC-Date": "2023-12-05T22:01:48Z",
"WARC-IP-Address": "159.203.75.59",
"WARC-Identified-Payload-Type": "text/html",
"WARC-Payload-Digest": "sha1:DE5UEGZNLXRVVE6MDUEC2TM32IBX3LOE",
"WARC-Record-ID": "<urn:uuid:9af3532c-c378-4637-ba18-d35681f94b8c>",
"WARC-Target-URI": "https://forum.literatureandlatte.com/t/images-stored-sideways/5794",
"WARC-Truncated": null,
"WARC-Type": "response",
"WARC-Warcinfo-ID": "<urn:uuid:771e0064-3fd1-4ff4-a3d3-f9da944efdaf>"
},
"warc_info": "isPartOf: CC-MAIN-2023-50\r\npublisher: Common Crawl\r\ndescription: Wide crawl of the web for November/December 2023\r\noperator: Common Crawl Admin (info@commoncrawl.org)\r\nhostname: ip-10-67-67-150\r\nsoftware: Apache Nutch 1.19 (modified, https://github.com/commoncrawl/nutch/)\r\nrobots: checked via crawler-commons 1.5-SNAPSHOT (https://github.com/crawler-commons/crawler-commons)\r\nformat: WARC File Format 1.1\r\nconformsTo: https://iipc.github.io/warc-specifications/specifications/warc-format/warc-1.1/"
}
|
{
"line_start_idx": [
0,
23,
24,
126,
127,
143,
489,
490,
573,
574,
665,
666,
918,
919,
1363,
1364,
1378,
1384,
1385,
1461,
1462,
1796,
1797,
2068,
2069,
2077,
2078,
2092,
2098,
2099,
2132,
2140,
2141,
2351,
2352,
2616,
2617,
2623,
2624,
3104,
3105,
3119,
3125,
3126,
3311
],
"line_end_idx": [
23,
24,
126,
127,
143,
489,
490,
573,
574,
665,
666,
918,
919,
1363,
1364,
1378,
1384,
1385,
1461,
1462,
1796,
1797,
2068,
2069,
2077,
2078,
2092,
2098,
2099,
2132,
2140,
2141,
2351,
2352,
2616,
2617,
2623,
2624,
3104,
3105,
3119,
3125,
3126,
3311,
3318
]
}
|
{
"red_pajama_v2": {
"ccnet_original_length": 3318,
"ccnet_original_nlines": 44,
"rps_doc_curly_bracket": 0,
"rps_doc_ldnoobw_words": 0,
"rps_doc_lorem_ipsum": 0,
"rps_doc_stop_word_fraction": 0.48741722106933594,
"rps_doc_ut1_blacklist": 0,
"rps_doc_frac_all_caps_words": 0.037086088210344315,
"rps_doc_frac_lines_end_with_ellipsis": 0,
"rps_doc_frac_no_alph_words": 0.16291390359401703,
"rps_doc_frac_unique_words": 0.4285714328289032,
"rps_doc_mean_word_length": 4.295680999755859,
"rps_doc_num_sentences": 48,
"rps_doc_symbol_to_word_ratio": 0,
"rps_doc_unigram_entropy": 5.031419277191162,
"rps_doc_word_count": 602,
"rps_doc_frac_chars_dupe_10grams": 0,
"rps_doc_frac_chars_dupe_5grams": 0,
"rps_doc_frac_chars_dupe_6grams": 0,
"rps_doc_frac_chars_dupe_7grams": 0,
"rps_doc_frac_chars_dupe_8grams": 0,
"rps_doc_frac_chars_dupe_9grams": 0,
"rps_doc_frac_chars_top_2gram": 0.011600930243730545,
"rps_doc_frac_chars_top_3gram": 0.011600930243730545,
"rps_doc_frac_chars_top_4gram": 0.01740138977766037,
"rps_doc_books_importance": -361.01434326171875,
"rps_doc_books_importance_length_correction": -361.01434326171875,
"rps_doc_openwebtext_importance": -217.2639923095703,
"rps_doc_openwebtext_importance_length_correction": -217.2639923095703,
"rps_doc_wikipedia_importance": -172.12860107421875,
"rps_doc_wikipedia_importance_length_correction": -172.12860107421875
},
"fasttext": {
"dclm": 0.018959399312734604,
"english": 0.9558162689208984,
"fineweb_edu_approx": 1.6899707317352295,
"eai_general_math": 0.8209118843078613,
"eai_open_web_math": 0.43091684579849243,
"eai_web_code": 0.12342441082000732
}
}
|
{
"free_decimal_correspondence": {
"primary": {
"code": "005.4",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Computer programming"
}
},
"secondary": {
"code": "006.6",
"labels": {
"level_1": "General works, books and libraries, information sciences",
"level_2": "",
"level_3": "Cognitive science"
}
}
},
"bloom_cognitive_process": {
"primary": {
"code": "3",
"label": "Apply"
},
"secondary": {
"code": "2",
"label": "Understand"
}
},
"bloom_knowledge_domain": {
"primary": {
"code": "3",
"label": "Procedural"
},
"secondary": {
"code": "2",
"label": "Conceptual"
}
},
"document_type_v1": {
"primary": {
"code": "5",
"label": "Social/Forum"
},
"secondary": {
"code": "3",
"label": "Reference/Encyclopedic/Educational"
}
},
"extraction_artifacts": {
"primary": {
"code": "0",
"label": "No Artifacts"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"missing_content": {
"primary": {
"code": "0",
"label": "No missing content"
},
"secondary": {
"code": "-1",
"label": "Abstain"
}
},
"document_type_v2": {
"primary": {
"code": "18",
"label": "Q&A Forum"
},
"secondary": {
"code": "21",
"label": "Customer Support"
}
},
"reasoning_depth": {
"primary": {
"code": "2",
"label": "Basic Reasoning"
},
"secondary": {
"code": "3",
"label": "Intermediate Reasoning"
}
},
"technical_correctness": {
"primary": {
"code": "3",
"label": "Mostly Correct"
},
"secondary": {
"code": "4",
"label": "Highly Correct"
}
},
"education_level": {
"primary": {
"code": "1",
"label": "General Audience"
},
"secondary": {
"code": "2",
"label": "High School Level"
}
}
}
|
672f1e42c33a7f9846924a2431ea77df
|