text stringlengths 100 9.93M | category stringclasses 11
values |
|---|---|
# MITRE Shield知识库
## 介绍
起源于在网络安全对抗中可能有用的技术,MITRE希望Shield知识库可以根据防守者的具体需要,以多种方式使用,可以是操作手册(操定操作流程),也可以是一个防守标准(定标准参考)
## 作用
> 开展积极防御的技术的数据库,还描述了防御计划中常见的一些战术,然后将战术映射到可能有助于实现这些目标的活动
> 该知识库包括一个MITRE ATT&CK和Shield 技术之间的映射,以说明对手战术、技术和过程(TTP)引入的防御可能性。
>
> [1]
- 具有开展积极防御的技术的数据库
- 描述了防御计划中常见的一些战术,用于将战术映射到可能有助于实现这些目标的活... | sec-knowleage |
# T1589-003-收集目标组织身份信息-员工姓名
## 来自ATT&CK的描述
在入侵受害者之前,攻击者可能会收集雇员姓名,这些信息可以在目标定位期间使用。员工姓名用于导出电子邮件地址,以及帮助指导其他侦察工作或制作更可信的诱饵。
攻击者可以轻松地收集雇员姓名,因为它们很容易获得并且可以通过在线或其他可访问的数据集(例如:[社交媒体](https://contribute.knowledge.qihoo.net/detail/technique/T1593/001)或[搜索受害者拥有的网站](https://contribute.knowledge.qihoo.net/detail/technique/T1594))暴露给攻击... | sec-knowleage |
mke2fs
===
创建磁盘分区上的“etc2/etc3”文件系统
## 补充说明
**mke2fs命令** 被用于创建磁盘分区上的“etc2/etc3”文件系统。
### 语法
```shell
mke2fs(选项)(参数)
```
### 选项
```shell
-b<区块大小>:指定区块大小,单位为字节;
-c;检查是否有损坏的区块;
-f<不连续区段大小>:指定不连续区段的大小,单位为字节;
-F:不管指定的设备为何,强制执行mke2fs;
-i<字节>:指定"字节/inode"的比例;
-N<inode数>:指定要建立的inode数目;
-l<文件>:从指定的文件中,读取文件西中损坏区块的信息;
-L<标签>:设置文... | sec-knowleage |
.TH while 3tcl
.SH NAME
.B while - 在条件满足时重复的执行脚本
.SH 总览
.B while test body
.SH 描述
while 命令把 test 作为一个表达式来求值(用与 expr 求它的参数的值相同的方式)。这个表达式的值必须是一个正确的 boolean 值;如果它是真值则把 body 传递给 Tcl 解释器来执行它。一旦执行了 body 则再次求值 test ,并重复处理直到最终 test 求值出一个假 boolean 值。可以在 body 中执行 Continue 命令来终止这个循环的当前重复操作(iteration),并可以在 body 中执行 break 命令来导致 whi... | sec-knowleage |
---
title: CVE-2022-0492
---
<center><h1>CVE-2022-0492</h1><b>本文作者:一生热爱</b><br><br></center>
---
## 一、简介
当容器没有开启额外安全措施时,获得容器内root 权限即可逃逸到宿主机
漏洞产品: linux kernel - cgroup
## 二、环境搭建
```bash
git clone https://github.com/brant-ruan/metarget.git
cd metarget/
pip3 install -r requirements.txt
./metarget cnv install cve-202... | sec-knowleage |
# Python Deserialization
* In Python source code, look for:
* `cPickle.loads`
* `pickle.loads`
* `_pickle.loads`
* `jsonpickle.decode`
## Pickle
The following code is a simple example of using `cPickle` in order to generate an auth_token which is a serialized User object.
:warning: `import cPickle` will... | sec-knowleage |
#!/usr/bin/env python3
import asyncio
import json
import os
import signal
async def main():
futures = []
if 'SALT_MINION_CONFIG' in os.environ:
with open('/etc/salt/minion.d/minion.conf', 'w') as minion_file:
json.dump(json.loads(os.environ['SALT_MINION_CONFIG']), minion_file)
futu... | sec-knowleage |
.TH UTMP 5 " July 2, 1997
.PP
.SH "NAME[名称]
.PP
utmp, wtmp - 登 录 记 录(login records)
.SH "SYNOPSIS[总览]
.PP
#include
.SH "DESCRIPTION[描述]
.PP
\fButmp\fP 文 件 用 于 记 录 当 前 系 统 用 户 是 哪 些 人。
但 是 实 际 的 人 数 可 能 比 这 个 数 目 要 多 , 因 为 并 非 所 有 用 户 都 用 utmp 登 录。
.PP
\fB警告:\fP \fButmp\fP
必 须 置 为 不 可 写 , 因 为 很 多 系 统 程 序 ( 有 点 傻 的... | sec-knowleage |
# ZICO2:1
> 下载地址:https://download.vulnhub.com/zico/zico2.ova
## 实战演练
找到靶场IP:`192.168.32.154`

扫描对外端口
```
┌──(root💀kali)-[~/Desktop]
└─# nmap -sT -sV -p1-65535 192.168.32.154 ... | sec-knowleage |
原文 by [阿里先知](https://xz.aliyun.com/t/2524)
## 1. Windows 的应急事件分类
Windows 系统的应急事件,按照处理的方式,可分为下面几种类别:
* 病毒、木马、蠕虫事件
* Web 服务器入侵事件或第三方服务入侵事件
* 系统入侵事件,如利用 Windows 的漏洞攻击入侵系统、利用弱口令入侵、利用其他服务的漏洞入侵,跟 Web 入侵有所区别,Web 入侵需要对 Web 日志进行分析,系统入侵只能查看 Windows 的事件日志。
* 网络攻击事件(DDoS、ARP、DNS 劫持等)
## 2. 通用排查思路
> 入侵肯定会留下痕迹,另外重点强调的是不要一上来就各种查查查,... | sec-knowleage |
# Code
---
## 项目
### 重构
- [七年三次大重构,聊聊我的重构成长史](https://shuyi.tech/archives/my-refactor-experiment)
### 代码质量
- [代码腐烂可以避免的吗?](https://shuyi.tech/archives/talk-about-code-decay)
### 成本
- [研发团队资源成本优化实践](https://tech.meituan.com/2019/02/21/rd-team-resource-cost-optimization-practice.html)
---
## 团队
- [技术Leader一定要懂所有业务细节吗?](h... | sec-knowleage |
# 威胁检测模型
此处整理一些需要威胁检测模型。威胁检测提供威胁狩猎的“原料”,数据的检测质量、效率很大程度上会影响威胁狩猎的深度(检测的精确率)和广度(检测的覆盖率)。
## 协议、证书相关异常检测
- https证书相关异常检测
## 常规Web漏洞检测模型
- SQL Injection漏洞检测
- Weblogic漏洞检测
- XSS漏洞检测
- ..
## 远程控制检测模型
- Shellcode检测模型
- Webshell检测模型
- 未知木马远控检测
- 未知后门植入检测
## 行为检测相关模型
- 内网横向渗透检测
- 高隐蔽扫描行为检测
## 文件检测相关模型
- ... | sec-knowleage |
# Django Trunc(kind) and Extract(lookup_name) SQL注入漏洞(CVE-2022-34265)
[中文版本(Chinese version)](README.zh-cn.md)
Django在2022年7月4日发布了安全更新,修复了在数据库函数`Trunc()`和`Extract()`中存在的SQL注入漏洞。
参考链接:
- https://www.djangoproject.com/weblog/2022/jul/04/security-releases/
## 漏洞环境
启动一个Django 4.0.5版本的服务器:
```
docker compose up -d
``... | sec-knowleage |
# NewOverFlow-1
Binary Exploitation, 250 points
## Description:
> Okay now lets try mainpulating arguments.
```c
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <unistd.h>
#include <sys/types.h>
#include <stdbool.h>
#define BUFFSIZE 64
#define FLAGSIZE 64
bool win1 = false;
bool win2 = false;
void w... | sec-knowleage |
.TH PSFGETTABLE 1 "28 Oct 1997" "控制台工具" "Linux 用户手册"
.SH NAME
psfgettable \- 从控制台字体中提取出嵌入的Unicode字符表
.SH 总览
.B psfgettable
.I 字体文件 [输出文件]
.SH 描述
.B psfgettable
命令从一个 .psf 格式的控制台字体中提取出嵌入的
Unicode字符表, 以易读格式输入到一个ASCII文件, 该文件的格式
如同
.BR psfaddtable (1)
所使用的. 若字体文件名是单个破折号(\-),
则字体从标准输入读取.
.SH "另见"
.BR consolechars (8),
.BR ... | sec-knowleage |
# Hello Java Sec
## 简介
Hello Java Sec是一个java安全编码平台,可以为开发人员攻击具体的漏洞代码、代码运行结果以及修复代码。
## 安装
安装Java8
```
apt install openjdk-8-jdk
```
> 我使用Ubuntu20.04,默认是Java 11,需要切换到Java 8,参考[这里](https://computingforgeeks.com/how-to-set-default-java-version-on-ubuntu-debian/)
启动MySQL
```
docker run -p 3306:3306 -e MYSQL_ROOT_PASSWORD=12... | sec-knowleage |
## She said it doesn't matter (misc/stego, 100p)
### PL Version
[ENG](#eng-version)
W zadaniu dostajemy obrazek [png](./m100.png) z zepsutym nagłówkiem. Rozpakowujemy zawartość pliku i za pomocą pozyskanych pikseli tworzymy obrazek, w którym ukryta jest flaga. Musimy ustawić dobre wymiary obrazka, które różnią sie od o... | sec-knowleage |
# Hello Vue
### 环境配置
前面的章节已经说了具体怎么安装 这里就不提了
```
vue init webpack vuex-demo
```
#### 按照下面进行配置
```
liuenqing@liuenqing-PC:~/Documents$ vue init webpack vuex-demo
? Project name vuex-demo
? Project description A Vue.js project
? Author l552177239 <552177239@qq.com>
? Vue build standalone
? Use ESLint to lint your code? Ye... | sec-knowleage |
# Play Nice
Category: Crypto, 110 points
## Description
> Not all ancient ciphers were so bad... The flag is not in standard format.
A Python file was attached.
```python
#!/usr/bin/python3 -u
import signal
SQUARE_SIZE = 6
def generate_square(alphabet):
assert len(alphabet) == pow(SQUARE_SIZE, 2)
matrix = []
for i, ... | sec-knowleage |
# CouchDB Erlang distribution Remote Command Execution (CVE-2022-24706)
[中文版本(Chinese version)](README.zh-cn.md)
Apache CouchDB is an open-source document-oriented NoSQL database, implemented in Erlang.
Apache CouchDB is written in Erlang and so it has built-in support for distributed computing (clustering). The clu... | sec-knowleage |
# 0x00 简介
其实用python go等语言打包成exe来免杀非常不错,这里我使用python 其他语言类似,这种方式就是打包的文件很大
Python打包工具有三种py2exe、PyInstaller和cx_Freeze,我这里使用的是PyInstaller。
其实用python来加载shellcode 在2012之前国外都有人发过文章了,各种加载方式,有些但是执行不成功,所以我这里整理了几种
# 0x01 shellcode->python
python 执行shellcode主要用到模块ctypes来使用和C兼容的数据类型 以下是网络流传的执行shellcode的代码
1.
```
#!/usr/bin/python
im... | sec-knowleage |
version: '2'
services:
weblogic:
image: vulhub/weblogic:10.3.6.0-2017
ports:
- "7001:7001" | sec-knowleage |
# T1590-005-收集目标组织网络信息-IP地址
## 来自ATT&CK的描述
攻击者可能会事先收集攻击目标的IP地址信息。公共IP地址可能是按块分配给企业的,也可能是一系列连续地址分配给企业的。已分配IP地址信息可能包括各种细节信息,比如当前使用的IP地址。收集已分配的IP地址信息,攻击者可以了解当前在用的IP地址,也可能推导出攻击目标的其他细节,比如组织规模、地理位置、Internet服务提供商以及面向公众基础设施的部署位置/方式。
IP地址信息可能是攻击者通过[主动扫描](https://contribute.knowledge.qihoo.net/detail/technique/T1595)或[钓鱼](https:/... | sec-knowleage |
.\" auto-generated by docbook2man-spec $Revision: 1.1 $
.TH "CREATE OPERATOR" "7" "2003-11-02" "SQL - Language Statements" "SQL Commands"
.SH NAME
CREATE OPERATOR \- 定义一个新的操作符
.SH SYNOPSIS
.sp
.nf
CREATE OPERATOR \fIname\fR (
PROCEDURE = \fIfuncname\fR
[, LEFTARG = \fIlefttype\fR ] [, RIGHTARG = \fIrighttype\fR... | sec-knowleage |
# Rescue Shell, 100p, exploit
In this task we were given a binary showing a password prompt. There was a
simple buffer overflow, allowing us to ROP and first dump GOT `fread` address, then
overwrite it with libc single gadget offset. | sec-knowleage |
version: '2'
services:
weblogic:
image: vulhub/weblogic:12.2.1.3-2018
ports:
- "7001:7001" | sec-knowleage |
# CyberTank Research
Miscellaneous
A PDF file was attached.
## Author (25 points)
> A secret document of CyberTank has leaked on the Internet, disclosing information on their latest research.
>
> Can you find out the author?
>
> Flag format: author name
If we open the file with a PDF reader, we get a 2-page document ... | sec-knowleage |
'\"
'\" Copyright (c) 1993 The Regents of the University of California.
'\" Copyright (c) 1994-1997 Sun Microsystems, Inc.
'\"
'\" See the file "license.terms" for information on usage and redistribution
'\" of this file, and for a DISCLAIMER OF ALL WARRANTIES.
'\"
'\" RCS: @(#) $Id: fcopy.n,v 1.2 2003/11/24 05:09:59 ... | sec-knowleage |
#!/usr/bin/python
import sys
import hashlib
import logging
import SocketServer
import base64
from flag import secret
from checksum_gen import WinternizChecksum
logger = logging.getLogger()
logger.setLevel(logging.INFO)
ch = logging.StreamHandler(sys.stdout)
ch.setFormatter(logging.Formatter("%(asctime)s - %(levelname... | sec-knowleage |
---
title: 一键执行三要素
---
## 在阿里云上一键执行三要素
使用 `-b` 命令一键执行三要素命令,快速证明权限获取,方便 HVV
```bash
cf alibaba ecs exec -b
```
指定单个实例获取三要素
```bash
cf alibaba ecs exec -b -i i-abcdefghijklmn
```
## 在腾讯云上一键执行三要素
### 云服务器
```bash
cf tencent cvm exec -b
```
### 轻量应用服务器
```bash
cf tencent lh exec -b
```
<Vssue />
<script>
export default {
... | sec-knowleage |
vgreduce
===
从卷组中删除物理卷
## 补充说明
**vgreduce命令** 通过删除LVM卷组中的物理卷来减少卷组容量。不能删除LVM卷组中剩余的最后一个物理卷。
### 语法
```shell
vgreduce(选项)(参数)
```
### 选项
```shell
-a:如果命令行中没有指定要删除的物理卷,则删除所有的空物理卷;
--removemissing:删除卷组中丢失的物理卷,使卷组恢复正常状态。
```
### 参数
* 卷组:指定要操作的卷组名称;
* 物理卷列表:指定要删除的物理卷列表。
### 实例
使用vgreduce命令从卷组"vg2000"中移除物理卷`/dev/sdb2`。在命令行... | sec-knowleage |
package com.hacker101.level13;
import android.net.Uri;
import android.os.Bundle;
import android.support.v7.app.AppCompatActivity;
import android.webkit.WebView;
import android.webkit.WebViewClient;
import java.math.BigInteger;
import java.nio.charset.StandardCharsets;
import java.security.MessageDigest;
import java.se... | sec-knowleage |
---
title: Automater
categories: Information Gathering
tags: [information gathering,kali linux,automater]
date: 2016-10-19 02:31:51
---
0x00 Automater介绍
-------------
Automater是一个URL /域,IP地址和Md5哈希开源情报工具,旨在为入侵分析师使分析过程更容易。 给定一个目标(URL,IP或HASH)或一个完整的目标文件,Automater将返回来自如下来源的相关结果:IPvoid.com,Robtex.com,Fortiguard.com,unshorte... | sec-knowleage |
lprm
===
删除打印队列中的打印任务
## 补充说明
**lprm命令** 用于删除打印队列中的打印任务。尚未完成的打印机任务会被放在打印机贮列之中,这个命令可用来将常未送到打印机的任务取消。
### 语法
```shell
lprm(选项)(参数)
```
### 选项
```shell
-E:与打印服务器连接时强制使用加密;
-P:指定接受打印任务的目标打印机;
-U:指定可选的用户名。
```
### 参数
打印任务:指定需删除的打印任务号。
### 实例
将打印机hpprint中的第102号任务移除:
```shell
lprm -Phpprint 102
```
将第101号任务由预设打印机中移除:
```s... | sec-knowleage |
### 堆相关数据结构
堆的操作就这么复杂,那么在 glibc 内部必然也有精心设计的数据结构来管理它。与堆相应的数据结构主要分为
- 宏观结构,包含堆的宏观信息,可以通过这些数据结构索引堆的基本信息。
- 微观结构,用于具体处理堆的分配与回收中的内存块。
### 堆相关微观结构malloc_chunk概述
在程序的执行过程中,我们称由 malloc 申请的内存为 chunk 。这块内存在 ptmalloc 内部用 malloc_chunk 结构体来表示。当程序申请的 chunk 被 free 后,会被加入到相应的空闲管理列表中。
非常有意思的是,**无论一个 chunk 的大小如何,处于分配状态还是释放状态,它们都使用一个统一的结... | sec-knowleage |
---
title: Android Studio
date: 2022-11-23 16:23:31.704217
background: bg-[#6bd488]
label:
tags:
-
-
categories:
- Keyboard Shortcuts
intro: |
A visual cheat-sheet for the 130 keyboard shortcuts found in the Andriod Studio software
---
Keyboard Shortcuts
------------------
### General
Shortcut | Act... | sec-knowleage |
---
title: TickTick
date: 2022-11-23 16:23:31.696573
background: bg-[#526ac9]
label:
tags:
-
-
categories:
- Keyboard Shortcuts
intro: |
A visual cheat-sheet for the 25 keyboard shortcuts found in the TickTick desktop app
---
Keyboard Shortcuts
------------------
### General I
Shortcut | Action
---|... | sec-knowleage |
# 0x00 ssh登陆
当内网有Linux时 Cobalt Strike也是考虑到的提供了ssh连接,只需要用目标机的beacon去连接就可以了。
1. 密码直接连接
```
beacon> help ssh
Use: ssh [target:port] [user] [pass]
Spawn an SSH client and attempt to login to the specified target
```
2. ssh-key
```
beacon> help ssh-key
Use: ssh [target:port] [user] [/path/to/key.pem]
Spawn an SSH client and... | sec-knowleage |
## 生命周期函数
当通过调用 React.createClass() 来创建组件的时候,你应该提供一个包含 render 方法的对象,并且也可以包含其它的在这里描述的生命周期方法。
### 首次加载时触发的生命周期
```
class App extends React.Component{
constructor(){
super()
console.log('constructor')
}
componentWillMount(){
console.log('will Mount')
}
componentDidMount(){
console.log('did Mount')
}
render... | sec-knowleage |
# Dragon CTF Teaser 2019
Team: c7, akrasuski1, nazywam, chivay, rodbert, Eternal, sasza, rev, shalom
### Table of contents
* [RMS (web/pwn)](rms)
* [ummmfpu (re)](ummmfpu)
* [RSA Chained (crypto)](rsachained)
* [Looking glas (web/crypto)](lookingglass) | sec-knowleage |
'\"
'\" Copyright (c) 1993 The Regents of the University of California.
'\" Copyright (c) 1994-1996 Sun Microsystems, Inc.
'\"
'\" See the file "license.terms" for information on usage and redistribution
'\" of this file, and for a DISCLAIMER OF ALL WARRANTIES.
'\"
'\" RCS: @(#) $Id: format.n,v 1.2 2003/11/24 05:09:59... | sec-knowleage |
## 迭代器(Iterator)
### Intent
提供一种顺序访问聚合对象元素的方法,并且不暴露聚合对象的内部表示。
### Class Diagram
- Aggregate 是聚合类,其中 createIterator() 方法可以产生一个 Iterator;
- Iterator 主要定义了 hasNext() 和 next() 方法;
- Client 组合了 Aggregate,为了迭代遍历 Aggregate,也需要组合 Iterator。
<div align="center"> <img src="https://cs-notes-1256109796.cos.ap-guangzhou.myqcloud.com... | sec-knowleage |
# Broken Link Hijacking
## Introduction
Broken Link Hijacking exists whenever a target links to an expired domain or page
## How to find
1. Manually find external links on the target site (For example, check some links to social media accounts)
2. Try using tools to find broken link, for example using tools that listed... | sec-knowleage |
version: '2'
services:
web:
image: vulhub/confluence:7.4.10
ports:
- "8090:8090"
depends_on:
- db
db:
image: postgres:12.8-alpine
environment:
- POSTGRES_PASSWORD=postgres
- POSTGRES_DB=confluence | sec-knowleage |
# 七、CRLF 注入
> 作者:Peter Yaworski
> 译者:[飞龙](https://github.com/)
> 协议:[CC BY-NC-SA 4.0](http://creativecommons.org/licenses/by-nc-sa/4.0/)
CRLF 注入是一类漏洞,在用户设法向应用插入 CRLF 时出现。在多种互联网协议中,包括 HTML,CRLF 字符表示了行的末尾,通常表示为`\r\n`,编码后是`%0D%0A`。在和 HTTP 请求或响应头组合时,这可以用于表示一行的结束,并且可能导致不同的漏洞,包括 HTTP 请求走私和 HTTP 响应分割。
对 HTTP 请求走私而言,它通常在 HTTP ... | sec-knowleage |
# Writeup InsomniHack Teaser CTF 2016
Team: cr019283, c7f.m0d3, msm, Rev, other019, nazywam, Shalom
### Table of contents
* [Fridginator 10K (Crypto/Web) 200](crypto_200_fridginator)
* [Toasted (Pwn) 250](pwn_250_toasted)
* [Smartcat (Web) 100](web_100_smartcat)
* [Greenbox (Web) 300](web_300_greenbox)
* [Bring the noi... | sec-knowleage |
#2020移动安全事记
时间线
- 0x00
- 1.1 [Rancor组织东南亚攻击活动分析](https://www.freebuf.com/articles/network/223258.html)
- 1.2 [这款流行聊天APP,居然是一个国家的监听工具](https://www.freebuf.com/articles/terminal/223811.html)
- 1.2 [机器学习之KNN检测恶意流量](https://www.freebuf.com/articles/web/223056.html)
- 1.2 [在Tesla Model S上实现Wi-Fi协议栈漏洞的利用](http://keenlab.... | sec-knowleage |
.\"
.\" Memory.man
.\"
.\" Extended Tcl memory leak locator.
.\"----------------------------------------------------------------------------
.\" Copyright 1992-1999 Karl Lehenbauer and Mark Diekhans.
.\"
.\" Permission to use, copy, modify, and distribute this software and its
.\" documentation for any purpose and with... | sec-knowleage |
#!/usr/bin/python
# nc 52.78.36.66 82
def solver(str1,str2):
finalstr = str1 + '==' + str2
result = True
tab = [[0,1] if x in finalstr else [0] for x in ['A','B','C','D','E','F','G','H','I']]
for A in tab[0]:
for B in tab[1]:
for C in tab[2]:
for D in tab[3]:
for E in tab[4]:
for F in tab[5]:
... | sec-knowleage |
# REdQueen
* Category: Web
* 400 Points
* Solved by the JCTF Team
## Description
> Revolution is about to start
> Enter! take a part
> Do you ready to test what is within your heart?
>
> Quenched in the search of knowing
> Under the path you should not be slowing
> Elders know, but they are toying
> Entrusted with the... | sec-knowleage |
# Spring Data Rest 远程命令执行漏洞(CVE-2017-8046)
Spring Data REST是一个构建在Spring Data之上,为了帮助开发者更加容易地开发REST风格的Web服务。在REST API的Patch方法中(实现[RFC6902](https://tools.ietf.org/html/rfc6902)),path的值被传入`setValue`,导致执行了SpEL表达式,触发远程命令执行漏洞。
参考链接:
- http://xxlegend.com/2017/09/29/Spring%20Data%20Rest服务器PATCH请求远程代码执行漏洞CVE-2017-8046补充分析/
-... | sec-knowleage |
import Crypto
from Crypto.PublicKey import RSA
import threading
import socket
import sys
import os
# e = 8257e5269cc0cdb32271154d4f5df508380e27b8826798c7271a237ff9e4191cc047629cf9684703f4826df1c69a1cfe786841d191757515abfe1a09d8bef7d92b40c6b37377e3218b109cfa734802ec418c2e08468ffcf6c11a1314600fce6714fa10fb3d5ed4a7ca89d6... | sec-knowleage |
import hashlib
def md5(s):
m=hashlib.md5()
m.update(s)
return m.hexdigest()
def hash(s):
return md5(md5(s)+"SALT")
def isnum(s):
for c in s:
if c not in "0123456789":
return False
return True
i=0
while True:
i+=1
h=hash(str(i))
if h[:2]=="0e" and isnum(h[2:]):... | sec-knowleage |
# IMF
> https://download.vulnhub.com/imf/IMF.ova
靶场IP:`192.168.32.175`

扫描对外端口
```
┌──(root💀kali)-[~/Desktop]
└─# nmap -p 1-65535 192.168.32.175 ... | sec-knowleage |
'\"
'\" Copyright (c) 1993 The Regents of the University of California.
'\" Copyright (c) 1994-1997 Sun Microsystems, Inc.
'\"
'\" See the file "license.terms" for information on usage and redistribution
'\" of this file, and for a DISCLAIMER OF ALL WARRANTIES.
'\"
'\" RCS: @(#) $Id: history.n,v 1.2 2003/11/24 05:09:5... | sec-knowleage |
# Fireplace (reverse, ppc, 763p)
> As it is in love and war, all is fair during the elections, especially when it comes to an opportunity to get rid of a candidate who is three points ahead of you. Your secret agent in this candidate’s campaign office informed you of some secret documents which prove that your rival is... | sec-knowleage |
## 模板方法(Template Method)
### Intent
定义算法框架,并将一些步骤的实现延迟到子类。
通过模板方法,子类可以重新定义算法的某些步骤,而不用改变算法的结构。
### Class Diagram
<div align="center"> <img src="https://cs-notes-1256109796.cos.ap-guangzhou.myqcloud.com/ac6a794b-68c0-486c-902f-8d988eee5766.png"/> </div><br>
### Implementation
冲咖啡和冲茶都有类似的流程,但是某些步骤会有点不一样,要求复用那些相同步骤的代码。
<di... | sec-knowleage |
## 逆向工程模块
|Reverse Engineering||||||
|:-:|:-:|:-:|:-:|:-:|:-:|
|[apktool](apktool.md)|dex2jar| diStorm3| edb-debugger| jad|javasnoop|
|JD-GUI|OllyDbg|smali|Valgrind|YARA|| | sec-knowleage |
import sys
import time
import string
import json
import requests
guess = '-_' + string.digits + string.ascii_letters
session = requests.session()
session.headers = {
'Content-Type': 'application/json',
}
def reset_password(target: str, email: str):
payload = {
'msg': 'method',
'method': 'sen... | sec-knowleage |
# RSA 介绍
RSA 加密算法是一种非对称加密算法。在公开密钥加密和电子商业中 RSA 被广泛使用。RSA 是 1977 年由罗纳德·李维斯特(Ron Rivest)、阿迪·萨莫尔(Adi Shamir)和伦纳德·阿德曼(Leonard Adleman)一起提出的。RSA 就是他们三人姓氏开头字母拼在一起组成的。
RSA 算法的可靠性由极大整数因数分解的难度决定。换言之,对一极大整数做因数分解愈困难,RSA 算法愈可靠。假如有人找到一种快速因数分解的算法的话,那么用 RSA 加密的信息的可靠性就肯定会极度下降。但找到这样的算法的可能性是非常小的。如今,只有短的 RSA 密钥才可能被强力方式解破。到 2017 年为止,还没有任何可... | sec-knowleage |
version: '2'
services:
web:
image: vulhub/gitea:1.4.0
ports:
- "3000:3000"
- "20022:22" | sec-knowleage |
.\" Man page for octave-bug
.\"
.\" Copyright (C) 1996 - 2000 John W. Eaton
.\"
.\" This file is part of Octave.
.\"
.\" Octave is free software; you can redistribute it and/or modify it
.\" under the terms of the GNU General Public License as published by the
.\" Free Software Foundation; either version 2, or (at your... | sec-knowleage |
# Flaskcards and Freedom
Web exploitation, 900 points
## Description:
> There seem to be a few more files stored on the flash card server but we can't login. Can you?
## Solution:
This challenge linked to a website similar to the one in the [original challenge](Flaskcards.md), and in fact the solution was similar too.
... | sec-knowleage |
dhclient
===
动态获取或释放IP地址
## 补充说明
**dhclient命令** 使用动态主机配置协议动态的配置网络接口的网络参数。
### 语法
```shell
dhclient(选项)(参数)
```
### 选项
```shell
0:指定dhcp客户端监听的端口号;
-d:总是以前台方式运行程序;
-q:安静模式,不打印任何错误的提示信息;
-r:释放ip地址。
```
### 参数
网络接口:操作的网络接口。
### 实例
```shell
dhclient -r #释放IP
dhclient #获取IP
``` | sec-knowleage |
#
# Licensed to the Apache Software Foundation (ASF) under one or more
# contributor license agreements. See the NOTICE file distributed with
# this work for additional information regarding copyright ownership.
# The ASF licenses this file to You under the Apache License, Version 2.0
# (the "License"); you may not us... | sec-knowleage |
# Nginx 解析漏洞复现
Nginx解析漏洞复现。
版本信息:
- Nginx 1.x 最新版
- PHP 7.x最新版
由此可知,该漏洞与Nginx、php版本无关,属于用户配置不当造成的解析漏洞。
直接执行`docker compose up -d`启动容器,无需编译。
访问`http://your-ip/uploadfiles/nginx.png`和`http://your-ip/uploadfiles/nginx.png/.php`即可查看效果。
正常显示:

增加`/.php`后缀,被解析成PHP文件:

访问`http://your-i... | sec-knowleage |
'\"
'\" Copyright (c) 1993 The Regents of the University of California.
'\" Copyright (c) 1994-1996 Sun Microsystems, Inc.
'\"
'\" See the file "license.terms" for information on usage and redistribution
'\" of this file, and for a DISCLAIMER OF ALL WARRANTIES.
'\"
'\" RCS: @(#) $Id: linsert.n,v 1.2 2003/11/24 05:09:5... | sec-knowleage |
# Exposed Source Code
## Introduction
Source code intended to be kept server-side can sometimes end up being disclosed to users. Such code may contain sensitive information such as database passwords and secret keys, which may help malicious users formulate attacks against the application.
## Where to find
`-`
## How t... | sec-knowleage |
# 博客项目
### 环境配置
参考第二节:VUE 安装
```
vue init webpack vuex-demo
cd vuex-demo
npm install
npm run dev
```
### 结构调整
删除没用的代码
### 添加路由
利用 vue-router 添加路由 /post 及 post 下的 CommentBox 以及 PostBody
### 使用组件内部数据
在 CommentBox 组件中添加 data 数据 ,利用 {{ comment.text }} 拿到数据
```js
<template>
<div class="comment-box">
<ul>
<li v-f... | sec-knowleage |
.\" 版权所有(c) 1993 Michael Haardt (michael@moria.de), Fri Apr 2 11:32:09 MET DST 1993
.\"
.\" 这是免费的文档;你可以遵照自由软件基金会出版的GNU通用出版许可版本2或者更高版本的条例来重新发布和/或修改它.
.\"
.\" GNU通用出版许可中涉及到的"目标代码(object code)"和"可执行程序(executables)"可解释为任意文档格式化的输出或者排版系统,包括中间的和已输出的结果.
.\"
.\" 该文档的发布寄望于能够实用,但并不做任何担保;甚至也不提供隐含的商品性的保证或者针对特殊目的适用性.参见GNU通用版权许可以获知更... | sec-knowleage |
---
title: Dart
date: 2021-11-04 10:12:25
background: bg-[#58aee9]
tags:
- dart
- flutter
categories:
- Programming
intro: |
A Dart cheat sheet with the most important concepts, functions, methods, and more. A complete quick reference for beginners.
plugins:
- copyCode
---
Getting Started {.cols-2}
--... | sec-knowleage |
# RealWorld CTF Quals 2019
Team: c7, rev, chivay, Eternal, rodbert, sasza, shalom
### Table of contents
* [Bank (crypto)](bank)
* [Puzzle (re)](puzzle)
* [caidanti flag 1 (re, shellcode)](caidanti_flag_1)
* [caidanti flag 2 (pwn)](caidanti_flag_2) | sec-knowleage |
# 黑灰产基础设施
黑灰产的对抗,是偏向于业务安全的,乃至关联到针对网络攻击的攻防来说,我们都始终逃不开一个话题:成本。
成本是对抗的本质。技术设施是黑灰产团队实施的攻击的基础,本章节将整理一些黑灰产基础设施相关的内容。
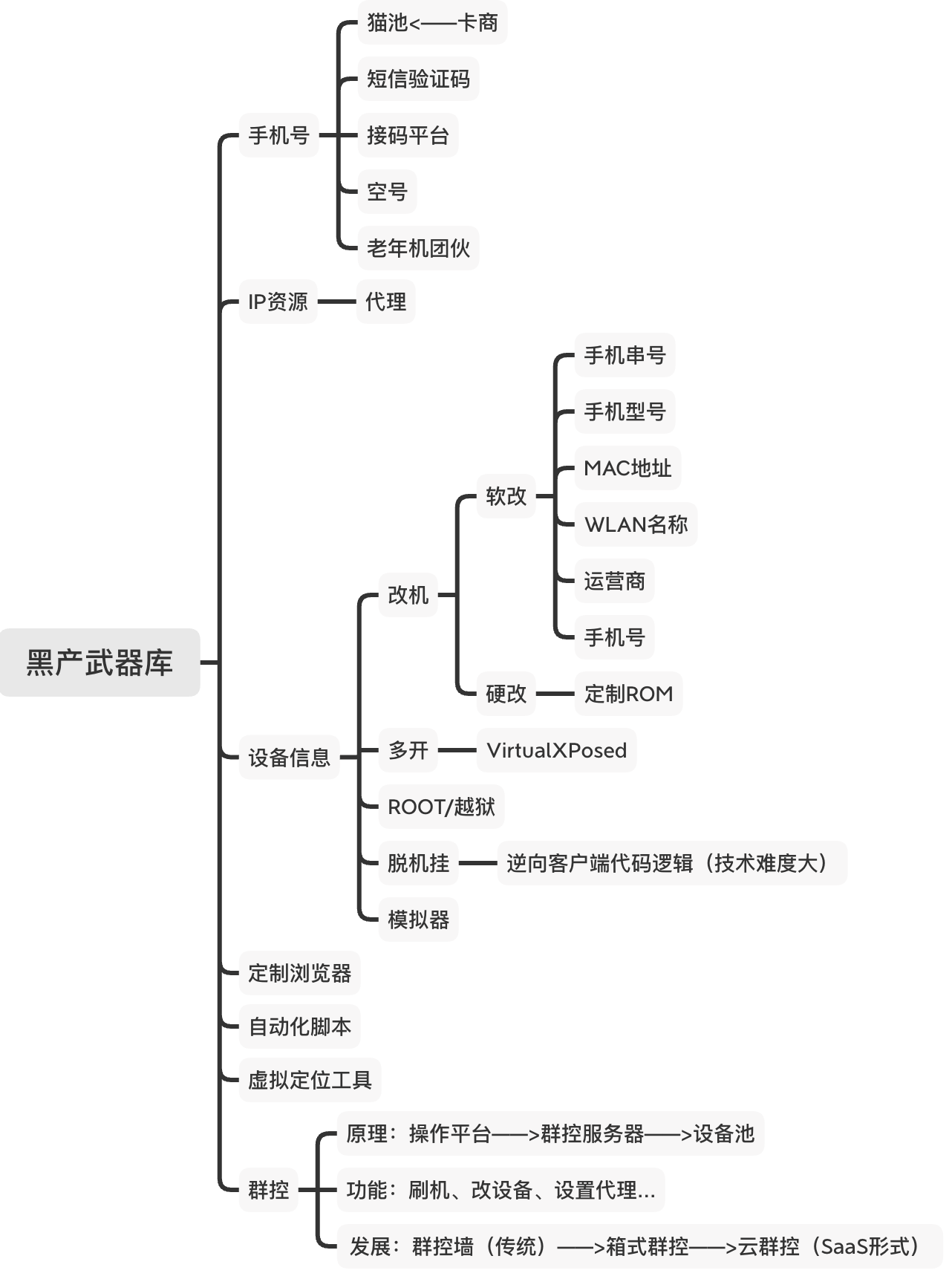
图:黑产基础设施,整理自《风控要略》一书 | sec-knowleage |
man
===
查看Linux中的指令帮助
## 补充说明
**man命令** 是Linux下的帮助指令,通过man指令可以查看Linux中的指令帮助、配置文件帮助和编程帮助等信息。
### 语法
```shell
man(选项)(参数)
```
### 选项
```shell
-a:在所有的man帮助手册中搜索;
-f:等价于whatis指令,显示给定关键字的简短描述信息;
-P:指定内容时使用分页程序;
-M:指定man手册搜索的路径。
```
### 参数
* 数字:指定从哪本man手册中搜索帮助;
* 关键字:指定要搜索帮助的关键字。
### 数字代表内容
```shell
1:用户在shell环境可操作... | sec-knowleage |
## Alexander Taylor (recon, 100p, 424 solves)
### PL Version
`for ENG version scroll down`
Dostajemy link od którego możemy wystartować `http://fuzyll.com/csaw2015/start`
Pod linkiem jest pierwsza zagadka:
`CSAW 2015 FUZYLL RECON PART 1 OF ?: Oh, good, you can use HTTP! The next part is at /csaw2015/<the acronym for my... | sec-knowleage |
# 10.3 跳台阶
## 题目链接
[牛客网](https://www.nowcoder.com/practice/8c82a5b80378478f9484d87d1c5f12a4?tpId=13&tqId=11161&tPage=1&rp=1&ru=/ta/coding-interviews&qru=/ta/coding-interviews/question-ranking&from=cyc_github)
## 题目描述
一只青蛙一次可以跳上 1 级台阶,也可以跳上 2 级。求该青蛙跳上一个 n 级的台阶总共有多少种跳法。
<div align="center"> <img src="https://cs-notes-125... | sec-knowleage |
# T1047-win-基于白名单WMIC执行payload
## 来自ATT&CK的描述
WMI(Windows Management Instrumentation)是Windows管理功能,它为本地和远程访问windows系统组件提供了统一的环境。它依赖WMI服务来进行本地和远程访问,以及SMB(服务器消息块)和RPCS(远程过程调用服务)来进行远程访问。RPCS通过端口135运行。
攻击者可能会使用WMI与本地和远程系统交互,也可能使用WMI来执行许多策略功能,例如为发现收集信息和远程执行文件来横向移动。
## 测试案例
WMIC扩展WMI(Windows Management Instrumentation,Windows... | sec-knowleage |
# 黑灰研究案例
此章节专门记录一些公开的黑灰产研究案例
## 事件追踪
- 东南亚博彩行业浮世绘,道尽黑产从业百态, 2020-04-02 By 红雨滴团队
https://ti.qianxin.com/blog/articles/southeast-asian-gaming-industry-research-report/
## 黑灰产团伙
- 金钻狗团伙(DiamondDog) | sec-knowleage |
# 知识图谱及其在安全领域的应用
## 1. 知识图谱是什么?
### 1.1 知识(Knowledge)是什么?
知识图谱(Knowledge Graph)正如其名,其本质是为了**表示知识**[1]。那么知识是该如何定义呢?我们来看一下维基百科中的定义:
> 知识是对某个主题确信的认识,并且这些认识拥有潜在的能力为特定目的而使用。意指透过经验或联想,而能够熟悉进而了解某件事情;这种事实或状态就称为知识,其包括认识或了解某种科学、艺术或技巧。此外,亦指透过研究、调查、观察或经验而获得的一整套知识或一系列资讯。
可以从这块相对抽象的定义里得到一个主观的感受,那就是知识是一种认知,其既是一种事实,也是一种状态。比如,“我会加减乘除... | sec-knowleage |
curl
===
利用URL规则在命令行下工作的文件传输工具
## 补充说明
**curl命令** 是一个利用URL规则在命令行下工作的文件传输工具。它支持文件的上传和下载,所以是综合传输工具,但按传统,习惯称curl为下载工具。作为一款强力工具,curl支持包括HTTP、HTTPS、ftp等众多协议,还支持POST、cookies、认证、从指定偏移处下载部分文件、用户代理字符串、限速、文件大小、进度条等特征。做网页处理流程和数据检索自动化,curl可以助一臂之力。
### 语法
```shell
curl(选项)(参数)
```
### 选项
```bash
-a --append ... | sec-knowleage |
.\" auto-generated by docbook2man-spec $Revision: 1.1 $
.TH "CREATE CAST" "7" "2003-11-02" "SQL - Language Statements" "SQL Commands"
.SH NAME
CREATE CAST \- 定义一个用户定义的转换
.SH SYNOPSIS
.sp
.nf
CREATE CAST (\fIsourcetype\fR AS \fItargettype\fR)
WITH FUNCTION \fIfuncname\fR (\fIargtype\fR)
[ AS ASSIGNMENT | AS IMPL... | sec-knowleage |
import string
import sys
from Crypto.Cipher import DES
import struct
import string
from pyasn1.codec.ber.encoder import encode
from pyasn1.codec.ber.decoder import decode
from requests import post
from re import search
def seven_to_eight(x):
[val] = struct.unpack("Q", x+"\x00")
out = 0
mask = 0b1111111
# ... | sec-knowleage |
# 安防设施搭建使用
<p align="center">
<img src="../../../../assets/img/banner/安防设施搭建使用.jpg" width="60%">
</p>
---
## 免责声明
`本文档仅供学习和研究使用,请勿使用文中的技术源码用于非法用途,任何人造成的任何负面影响,与本人无关.`
---
## 蜜罐
### Conpot
> 一个由 glaslos 等人开发的,用于获得关于工控系统的威胁情报的开源 ICS/SCADA 蜜罐
**项目地址**
- https://github.com/mushorg/conpot
**搭建过程**
```bash
docker pull ho... | sec-knowleage |
# T1591-001-收集目标组织信息-确定物理位置
## 来自ATT&CK的描述
攻击者可能会收集目标组织的实际位置,这些位置可以在目标锁定期间使用。有关目标组织的物理位置的信息可能包括各种详细信息,包括关键资源和基础结构的存放位置。实际位置还可以指示目标组织在哪个法律管辖区或机构内工作。
攻击者可以通过多种方式收集此信息,例如通过“网络钓鱼诱骗”直接诱捕。目标组织的实际位置也可能通过在线或其他可访问的数据集(例如:搜索受害人拥有的网站或社交媒体)暴露给攻击者。
## 测试案例
例如受害者的个人社交信息,微博、微信、QQ等。
例如受害组织的位置信息,通过官方网站即可查找到相关组织的位置。
## 检测日志
无
## 测试复现
无
... | sec-knowleage |
.\" Copyright (c) 1980, 1990 The Regents of the University of California.
.\" All rights reserved.
.\"
.\" Redistribution and use in source and binary forms, with or without
.\" modification, are permitted provided that the following conditions
.\" are met:
.\" 1. Redistributions of source code must retain the above co... | sec-knowleage |
**Authors**: < [nixawk](https://github.com/nixawk) >
----
# Books
## Penetration Testing Books
* [The Art of Exploitation by Jon Erickson, 2008](https://www.nostarch.com/hacking2.htm)
* [Metasploit: The Penetration Tester's Guide by David Kennedy et al., 2011](https://www.nostarch.com/metasploit)
* [Penetration Testing... | sec-knowleage |
# 55.2 平衡二叉树
[NowCoder](https://www.nowcoder.com/practice/8b3b95850edb4115918ecebdf1b4d222?tpId=13&tqId=11192&tPage=1&rp=1&ru=/ta/coding-interviews&qru=/ta/coding-interviews/question-ranking&from=cyc_github)
## 题目描述
平衡二叉树左右子树高度差不超过 1。
<div align="center"> <img src="https://cs-notes-1256109796.cos.ap-guangzhou.myqcloud.... | sec-knowleage |
cat
===
连接多个文件并打印到标准输出。
## 概要
```shell
cat [OPTION]... [FILE]...
```
## 主要用途
- 显示文件内容,如果没有文件或文件为`-`则读取标准输入。
- 将多个文件的内容进行连接并打印到标准输出。
- 显示文件内容中的不可见字符(控制字符、换行符、制表符等)。
## 参数
FILE(可选):要处理的文件,可以为一或多个。
## 选项
```shell
长选项与短选项等价
-A, --show-all 等价于"-vET"组合选项。
-b, --number-nonblank 只对非空行编号,从1开始编号,覆盖"-n"选项。
-e ... | sec-knowleage |
# Upload
---
## 免责声明
`本文档仅供学习和研究使用,请勿使用文中的技术源码用于非法用途,任何人造成的任何负面影响,与本人无关.`
---
**描述**
文件上传过程中,通常因为未校验上传文件后缀类型,导致用户可上传一些 webshell 文件。
**相关文章**
- [简单粗暴的文件上传漏洞](https://paper.seebug.org/560/)
- [BookFresh Tricky File Upload Bypass to RCE](https://secgeek.net/bookfresh-vulnerability/)
- [Upload_Attack_Framework](https://www... | sec-knowleage |
## HardToSay (misc, 200p, (111, 88, 73, 28) solves)
Ruby on Fails.
FLAG1: nc 54.199.215.185 9001
FLAG2: nc 54.199.215.185 9002
FLAG3: nc 54.199.215.185 9003
FLAG4: nc 54.199.215.185 9004
hard_to_say-151ba63da9ef7f11bcbba93657805f85.rb
### PL
[ENG](#eng-version)
Dostajemy taki kod:
```ruby
#!/us... | sec-knowleage |
# Security by Obscurity
Misc.
## Description:
> Reading the contents of the screenshot you find that some guy named "John" created the firmware for the OffHub router and stored it on an iDropDrive cloud share. You fetch it and find "John" packed the firmware with an unknown key. Can you recover the package key?
A binar... | sec-knowleage |
---
title: Kotlin
date: 2023-02-26 16:24:31
background: bg-[#7954f6]
tags:
- Cross-platform
- Android
categories:
- Programming
intro: |
A quick reference cheatsheet for Kotlin that includes usage, examples, and more.
plugins:
- copyCode
---
Introduction to Kotlin
----
### main()
```kotlin
fun main() {
p... | sec-knowleage |
# 固件安全
---
## 免责声明
`本文档仅供学习和研究使用,请勿使用文中的技术源码用于非法用途,任何人造成的任何负面影响,与本人无关.`
---
**相关教程**
- [G4rb3n/IoT_Sec_Tutorial](https://github.com/G4rb3n/IoT_Sec_Tutorial)
- [Home of Pierre](https://pierrekim.github.io/index.html)
**相关文章**
- [施耐德充电桩漏洞挖掘之旅](https://bacde.me/post/Schneider-Charging-Staiong-Vulnerabilites/)
```
... | sec-knowleage |
# reverse_cipher
Reverse Engineering, 300 points
## Description:
> We have recovered a binary and a text file. Can you reverse the flag.
## Solution:
Let's inspect the attached files:
```console
root@kali:/media/sf_CTFs/pico/reverse_cipher# file rev
rev: ELF 64-bit LSB pie executable x86-64, version 1 (SYSV), dynamica... | sec-knowleage |
import urllib
from PIL import Image
import io, re
handle = urllib.urlopen("http://ctfquest.trendmicro.co.jp:43210/click_on_the_different_color")
data = handle.read()
def extractLink(data):
x = re.search("window.location.href=(.*\\?)", data)
return x.group(1)[2:-1]
def getPixel(picture_path):
fd = urlli... | sec-knowleage |
.TH STAT 1 UNSUP
.UC 4
.SH NAME
stat \- 打印信息节点(inode)内容
.SH SYNOPSIS(总览)
.B stat
.I filename
.I [filenames ... ]
.SH DESCRIPTION(描述)
.PP
.I stat
打印出一个信息节点的内容,它们显示为对人可读的格式的\fIstat(2)\fR.
.PP
下面是\fIstat\fR的一个示例输出:
.nf
File: \*(lq/\*(rq
Size: 1024 Allocated Blocks: 2 Filetype: Directory
Mode: (0755/drwx... | sec-knowleage |
# tryMe
15 Points
## Solution
We get a page with a button "Send a test email". The developer console outputs a message: "Loading the code for the tryMe (15 pt) page. To debug this code, open o2txy.js in Developer Tools.".
Let's click the button. We get an email to the address we used for registration:
```
Hey firstName... | sec-knowleage |
systool
===
显示基于总线、类和拓扑显示系统中设备的信息
## 补充说明
**systool命令** 指令显示基于总线、类和拓扑显示系统中设备的信息。
### 语法
```shell
systool(选项)(参数)
```
### 选项
```shell
-a:显示被请求资源的属性;
-b<总线>:显示指定总线的信息;
-c<class>:显示指定类的信息;
-d:仅显示设备;
-h:显示指令的用法;
-m<模块名称>:显示指定模块的信息;
-p:显示资源的“sysfs”绝对路径;
-v:显示所有属性;
-A<属性>:显示请求资源的属性值;
-D:仅显示驱动程序信息;
-P:显示设备的父类。
```
### 参数
设... | sec-knowleage |
# Customer Service
* Category: Web
* 200 Points
* Solved by the JCTF Team
## Description
> Last year we decided to improve our customer service to our security researchers team by created an AI-based vulnerability scanner.
>
> Now it released for free to the community!
>
> We Hope you will like that!
## Solution
We ... | sec-knowleage |
# Dawn2
> https://download.vulnhub.com/sunset/dawn2.7z
靶场IP:`192.168.32.21`
扫描对外端口服务
```
┌──(root㉿kali)-[/tmp]
└─# nmap -p 1-65535 192.168.32.21
Starting Nmap 7.92 ( https://nmap.org ) at 2022-09-14 00:17 EDT
Nmap scan report for 192.168.32.21
Host is ... | sec-knowleage |
Subsets and Splits
Top 100 EPUB Books
This query retrieves a limited set of raw data entries that belong to the 'epub_books' category, offering only basic filtering without deeper insights.