text stringlengths 100 9.93M | category stringclasses 11
values |
|---|---|
#!/usr/bin/env python
# -*- coding: utf-8 -*-
# ---------------------------------------------------
# Copyright (c) 2013 Pablo Caro. All Rights Reserved.
# Pablo Caro <me@pcaro.es> - http://pcaro.es/
# AES_base.py
# ---------------------------------------------------
sbox = [99, 124, 119, 123, 242, 107, 111, 197, 48,... | sec-knowleage |
# M-Poly-Cipher (re/crypto, 279p, 26 solved)
In the challenge we get [a binary](cipher) to reverse.
We also get a [public key](public.key) and [encrypted flag](flag.enc).
After hours of blood, sweat and tears we finally reach a [working python implementation](code.py).
The key part is:
```python
def encrypt(pt_file: st... | sec-knowleage |
package org.vulhub;
import org.springframework.messaging.handler.annotation.MessageMapping;
import org.springframework.messaging.handler.annotation.SendTo;
import org.springframework.stereotype.Controller;
import org.springframework.web.util.HtmlUtils;
@Controller
public class GreetingController {
@MessageMappi... | sec-knowleage |
.TH USLEEP 1 "Red Hat, Inc" \" -*- nroff -*-
.SH NAME
usleep \- 睡眠若干微秒
.SH "总览 (SYNOPSIS)"
.B usleep
[\fInumber\fP]
.SH "描述 (DESCRIPTION)"
.B usleep
睡眠 指定的 微秒数. 缺省值 是 1.
.SH "选项 (OPTIONS)"
\fI--usage\fP
显示 简短 的 使用方法.
.TP
\fI--help, -?\fP
显示 帮助信息.
.TP
\fI-v, --version\fP
显示 版本信息.
.SH BUGS
在 许多 机器 上, 微秒 计数 不够 精确. 精度 只能 到... | sec-knowleage |
# come-and-git-it-2
* Category: DevSecOps
* 350 Points
* Solved by the JCTF Team
## Description
>
>
> 1. Add the attached ssh key to your ssh-agent. [Here's some documentation](https://docs.github.com/en/free-pro-team@latest/github/authenticating-to-github/generating-a-new-ssh-key-and-adding-it-to-the-ssh-agent#addin... | sec-knowleage |
ifstat
===
统计网络接口流量状态
## 补充说明
**ifstat命令** 就像iostat/vmstat描述其它的系统状况一样,是一个统计网络接口活动状态的工具。ifstat工具系统中并不默认安装,需要自己下载源码包,重新编译安装,使用过程相对比较简单。
### 下载
```shell
http://gael.roualland.free.fr/ifstat/ (官网)
wget http://gael.roualland.free.fr/ifstat/ifstat-1.1.tar.gz
```
### 编译安装
```shell
tar -zxvf ifstat-1.1.tar.gz
cd ifstat-1.... | sec-knowleage |
# arraymaster2
PWN
## Description:
> We improved our security with more mitigations.
A binary file and a libc file were attached.
## Solution:
This challenge is similar to [arraymaster1](arraymaster1.md), but `spawn_shell` was removed and several runtime protections were activated:
```console
root@kali:/media/sf_CTFs/3... | sec-knowleage |
# Loly
> https://download.vulnhub.com/loly/Loly.ova
靶场IP:`192.168.2.136`
扫描对外端口服务
```
┌──(root💀kali)-[~]
└─# nmap -p1-65535 -sV 192.168.2.136 ... | sec-knowleage |
# T1190-JumpServer v2.6.1 RCE攻击检测
## 来自ATT&CK的描述
使用软件,数据或命令来利用面向Internet的计算机系统或程序中的弱点,从而导致意外或无法预期的行为。系统的弱点可能是错误、故障或设计漏洞。这些应用程序通常是网站,但是可以包括数据库(例如SQL),标准服务(例如SMB 或SSH)以及具有Internet可访问开放的任何其他应用程序,例如Web服务器和相关服务。根据所利用的缺陷,这可能包括“利用防御防卫”。
如果应用程序托管在基于云的基础架构上,则对其进行利用可能会导致基础实际应用受到损害。这可以使攻击者获得访问云API或利用弱身份和访问管理策略的路径。
对于网站和数据库,OWASP排... | sec-knowleage |
'\" t
.TH "SYSTEMD\-SOCKET\-ACTIVATE" "1" "" "systemd 231" "systemd-socket-activate"
.\" -----------------------------------------------------------------
.\" * Define some portability stuff
.\" -----------------------------------------------------------------
.\" ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~... | sec-knowleage |
# XStream Deserialization Remote Command Execution (CVE-2021-21351)
[中文版本(Chinese version)](README.zh-cn.md)
XStream is a simple library to serialize objects to XML and back again.
XStream uses a blocklist mechanism when parsing XML text which is utilized to defend against deserialization vulnerabilities, but in 1.4... | sec-knowleage |
---
title: Sketch
date: 2022-11-23 16:23:31.699427
background: bg-[#d36f2b]
label: Mac
tags:
-
- mac
categories:
- Keyboard Shortcuts
intro: |
A visual cheat-sheet for the 149 keyboard shortcuts found in Sketch. This application is MacOS-only.
---
Keyboard Shortcuts
------------------
### General {.ro... | sec-knowleage |
continue
===
结束本次循环,继续执行下一个for,while或until循环。
## 概要
```shell
continue [n]
```
## 主要用途
- 结束本次循环,继续执行下一个for,while或until循环;可指定从第几层循环继续执行。
## 参数
n(可选):大于等于1的整数,用于指定从第几层循环继续执行。
## 返回值
返回状态为成功除非n小于1。
## 例子
```shell
# continue的可选参数n缺省值为1。
for((i=3;i>0;i--)); do
# 跳到内层for循环继续执行。
for((j=3;j>0;j--)); do
if((j==2)); then
... | sec-knowleage |
**注:**请多喝点热水或者凉白开,可预防**肾结石,通风**等。
痛风可伴发肥胖症、高血压病、糖尿病、脂代谢紊乱等多种代谢性疾病。
**攻击机:**
192.168.1.5 Debian
**靶机:**
192.168.1.2 Windows 7
192.168.1.115 Windows 2003
192.168.1.119 Windows 2003
**第一季主要介绍scanner下的五个模块,辅助发现内网存活主机,分别为:**
* auxiliary/scanner/discovery/arp_sweep
* auxiliary/scanner/discovery/udp_sweep
* auxiliary/sc... | sec-knowleage |
# CVP
CVP是Lattice-based cryptography中尤为重要的一个问题。
问题的基本定义如下:给定格$L$的一组基与向量$\mathbf{v}$,找到在$L$上离$\mathbf{v}$最近的一个向量。
<!--
TODO: Add more Lattice-based cryptography (CVP specifically) application intro here.
TODO: Make intro more descriptive and rigorous.
-->
## Algorithms
### Babai's nearest plane algorithm
<!--
TODO: Add ... | sec-knowleage |
# Cross Site Scripting
> Cross-site scripting (XSS) is a type of computer security vulnerability typically found in web applications. XSS enables attackers to inject client-side scripts into web pages viewed by other users.
## Summary
- [Cross Site Scripting](#cross-site-scripting)
- [Vulnerability Details](#vulnerab... | sec-knowleage |
# ffmpeg 任意文件读取漏洞环境
参考资料:
- http://bobao.360.cn/learning/detail/4032.html
- https://hackerone.com/reports/242831
- https://github.com/neex/ffmpeg-avi-m3u-xbin
## 环境搭建
编译及启动环境
```
docker compose build
docker compose up -d
```
环境启动后监听8080端口,访问`http://your-ip:8080/`即可查看。
## 漏洞利用
漏洞原理不再赘述,直接下载exp,并生成payload:
``... | sec-knowleage |
# Mini RSA
Category: Crypto, 70 points
## Description
> What happens if you have a small exponent? There is a twist though, we padded the plaintext so that (M ** e) is just barely larger than N.
>
> Let's decrypt this:
```
N:
16157656843214630540782260519598878842336783177348929017407633211352136367960754624019502746... | sec-knowleage |
# Welcome (re, 96p, 49 solved)
In the challege we get a [virtual machine code](vo-interpreter.c) and a [flag checking program](welcome_task.voprotected.c) implemented on this VM.
We're lazy so before trying to analyse VM or at least translate the challege code to some assembly-like representation, we simply compiled th... | sec-knowleage |
# hiecss (Crypto 150)
###ENG
[PL](#pl-version)
In the task we get [source code](hiecss.py) of some elliptic curve - based encryption scheme.
The most important part is:
```python
e = 65537
order = 'Give me the flag. This is an order!'
def decode(bs):
if len(bs) < 0x40:
return None
s, m = int(bs[:0x40], ... | sec-knowleage |
apachectl
===
Apache服务器前端控制工具
## 补充说明
**apachectl命令** 是Apache的Web服务器前端控制工具,用以启动、关闭和重新启动Web服务器进程。
### 语法
```
apachectl(参数)
```
### 参数
* configtest:检查设置文件中的语法是否正确;
* fullstatus:显示服务器完整的状态信息;
* graceful:重新启动Apache服务器,但不会中断原有的连接;
* help:显示帮助信息;
* restart:重新启动Apache服务器;
* start:启动Apache服务器;
* status:显示服务器摘要的状态信息;
* stop:停... | sec-knowleage |
# Ducking
Category: Steganography, 50 points
## Description
> I hid a flag in my favorite photo, try to find it! 🦆🦆🦆
An image was attached.
## Solution
We start by searching for strings within the attached image:
```console
┌──(user@kali)-[/media/sf_CTFs/ducky_debug_duck/Ducking]
└─$ strings ducking.jpg -n 10
pass... | sec-knowleage |
import random
class MT19937Recover:
"""Reverses the Mersenne Twister based on 624 observed outputs.
The internal state of a Mersenne Twister can be recovered by observing
624 generated outputs of it. However, if those are not directly
observed following a twist, another output is required to restore ... | sec-knowleage |
package com.p000a;
import java.util.Arrays;
public class CheckReal {
private static int[] f0a = new int[]{-1414812757, -842150451, -269488145, 305419896};
private static byte[] f1b = new byte[]{(byte) 99, (byte) 124, (byte) 101, (byte) -23, (byte) -114, (byte) 81, (byte) -47, (byte) -39, (byte) -102, (byte) 7... | sec-knowleage |
#!/usr/bin/python
# https://www.insomniasec.com/downloads/publications/LFI%20With%20PHPInfo%20Assistance.pdf
# The following line is not required but supposedly optimizes code.
# However, this breaks on some Python 2 installations, where the future module version installed is > 0.16. This can be a pain to revert.
# ... | sec-knowleage |
# Django QuerySet.order_by() SQL注入漏洞(CVE-2021-35042)
Django在2021年7月1日发布了一个安全更新,修复了在QuerySet底下的order_by函数中存在的SQL注入漏洞
参考链接:
- https://www.djangoproject.com/weblog/2021/jul/01/security-releases/
该漏洞需要用户可控order_by传入的值,在预期列的位置注入SQL语句。
## 漏洞环境
执行如下命令编译及启动一个存在漏洞的Django 3.2.4:
```
docker compose build
docker compose up ... | sec-knowleage |
# 权限提升
> 部分内容由 [the-fog](https://github.com/the-fog) 提供,仅做部分内容排版修改
---
## 免责声明
`本文档仅供学习和研究使用,请勿使用文中的技术源码用于非法用途,任何人造成的任何负面影响,与本人无关.`
---
## 大纲
* **[Win](#win)**
* **[Linux](#linux)**
* **[Mysql](#mysql)**
* **[MSSQL](#mssql)**
* **[PostgreSQL](#postgresql)**
* **[Redis](#redis)**
---
**多平台提权辅助工具**
- [carlospolop/privile... | sec-knowleage |
---
title: Markdown
date: 2020-12-14 18:28:43
background: bg-[#6319bf]
tags:
- md
- Markup
- text
- format
categories:
- Programming
intro: This is a quick reference cheat sheet to the Markdown syntax.
plugins:
- copyCode
---
Markdown Quick Reference
---------------
### Headers (atx style)
```ma... | sec-knowleage |
# Tomcat Arbitrary Write-file Vulnerability through PUT Method (CVE-2017-12615)
[中文版本(Chinese version)](README.zh-cn.md)
Tomcat version: 8.5.19
## Environment Setup
```
docker compose build
docker compose up -d
```
After successfully running the commands above, you will see the example page of Tomcat through visit... | sec-knowleage |
'\"
'\" Copyright (c) 1997 Sun Microsystems, Inc.
'\"
'\" See the file "license.terms" for information on usage and redistribution
'\" of this file, and for a DISCLAIMER OF ALL WARRANTIES.
'\"
'\" RCS: @(#) $Id: dde.n,v 1.2 2003/11/24 05:09:59 bbbush Exp $
'\"
'\" The definitions below are for supplemental macros use... | sec-knowleage |
.\" DO NOT MODIFY THIS FILE! It was generated by help2man 1.48.5.
.\"*******************************************************************
.\"
.\" This file was generated with po4a. Translate the source file.
.\"
.\"*******************************************************************
.TH CHOWN 1 2022年9月 "GNU coreutils 9.... | sec-knowleage |
# RAR
---
* RAR 文件头 `52 61 72 21 1A 07 00`
* RAR 文件尾 `C4 3D 7B 00 40 07 00`
---
Rar 文件主要由标记块,压缩文件头块,文件头块,结尾块组成。
其每一块大致分为以下几个字段:
| 名称 | 大小 | 描述 |
| - | - | - |
| HEAD_CRC | 2 | 全部块或块部分的CRC |
| HEAD_TYPE | 1 | 块类型 |
| HEAD_FLAGS | 2 | 阻止标志 |
| HEAD_SIZE | 2 | 块大小 |
| ADD_SIZE | 4 | 可选字段 - 添加块大小 |
Rar ... | sec-knowleage |
---
title: SSH
date: 2021-01-27 11:48:05
background: bg-blue-400
tags:
- protocol
- remote
- network
- 22
categories:
- Linux Command
intro: |
This quick reference cheat sheet provides various for using SSH.
plugins:
- copyCode
---
Getting Started
---------------
### Connecting
Connect to a ... | sec-knowleage |
# T1014-win-Rootkit
## 来自ATT&CK的描述
攻击者可能使用rootkits来隐藏程序、文件、网络连接、服务、驱动程序和其他系统组件的存在。Rootkits是通过拦截、钩住和修改提供系统信息的操作系统API调用来隐藏恶意软件的存在的程序。
Rootkits或启用Rootkit的功能可能存在于操作系统的用户或内核层面,或更低的层面,包括管理程序、主引导记录或系统固件。在Windows、Linux和Mac OS X系统中,已经出现了rootkits。
## 测试案例
Windows签名的驱动程序 Rootkit测试
该测试利用已签名的驱动程序在Kernel中执行代码。这个例子来自一个博客,它利用puppetst... | sec-knowleage |
# Document with secrets
Category: Web
## Description
> Part 6 of Imperva's challenge
>
> To be a good web application penetration tester, you need to notice the small things? What can go wrong when a file is uploaded?
>
## Solution
The [previous challenge](Bleeding_cloud.md)'s flag has left us with a hint: `docx_are_... | sec-knowleage |
# T1120-win-周边设备发现
## 来自ATT&CK的描述
攻击者可能试图收集有关连接到计算机系统的外围设备和组件的信息。外围设备可以包括支持各种功能的辅助资源,如键盘、打印机、照相机、智能卡读卡器或可移动存储。这些信息可用于提高他们对系统和网络环境的认识,或可用于进一步的行动。
## 测试案例
fsutil-fsinfo命令列出所有驱动器、查询驱动器类型、查询卷信息、查询特定于 NTFS 的卷信息或查询文件系统统计信息。
fsutil fsinfo drivetype C:
可能的结果为:
未知驱动器
没有这样的根目录
可移动驱动器,如软驱
固定驱动器
远程/网络驱动器
CD-ROM 驱动器
Ram 磁盘
## 检测日志
... | sec-knowleage |
# S2-012 Remote Code Execution Vulnerablity
[中文版本(Chinese version)](README.zh-cn.md)
Affected Version: 2.1.0 - 2.3.13
Details: http://struts.apache.org/docs/s2-012.html
## Reference
If the redirect type is used when configuring `result` in the `action`, and ${param_name} is also used as the redirect variable, for ... | sec-knowleage |
# Magic test (Web)
In the task we get a very simple webpage where we can input a name and birthday.
We get source code of the server part as well:
```javascript
const express = require('express')
const app = express()
function getTimestamp(date) {
try{
var x = Math.floor((new Date(date)) / 1000);
re... | sec-knowleage |
# Somewhat OTP
Category: Cryptography, 250 points
## Description
> Oh no! EEvil department managed to get an hold on our computers and encrypted all of our files! We know from last time that their cryptography skills are not the best, see if you can reverse the encryption, you might even get a flag...
A binary file was... | sec-knowleage |
# libssh 服务端权限认证绕过漏洞(CVE-2018-10933)
libssh是一个提供ssh相关接口的开源库,包含服务端、客户端等。其服务端代码中存在一处逻辑错误,攻击者可以在认证成功前发送`MSG_USERAUTH_SUCCESS`消息,绕过认证过程,未授权访问目标SSH服务器。
参考资料:
- https://www.libssh.org/security/advisories/CVE-2018-10933.txt
- https://www.seebug.org/vuldb/ssvid-97614
## 漏洞环境
执行如下命令启动存在漏洞的环境:
```
docker compose up -d
```
... | sec-knowleage |
# 例子
下面会介绍一些 CTF 中的格式化漏洞的题目。也都是格式化字符串常见的利用。
## 64位程序格式化字符串漏洞
### 原理
其实 64 位的偏移计算和 32 位类似,都是算对应的参数。只不过 64 位函数的前 6 个参数是存储在相应的寄存器中的。那么在格式化字符串漏洞中呢?虽然我们并没有向相应寄存器中放入数据,但是程序依旧会按照格式化字符串的相应格式对其进行解析。
### 例子
这里,我们以 2017 年的 UIUCTF 中 [pwn200 GoodLuck](https://github.com/ctf-wiki/ctf-challenges/tree/master/pwn/fmtstr/2017-UIUCTF-pwn... | sec-knowleage |
# Endgame
Category: Reversing, 300 Points
## Description
> This guy Thanos snapped his fingers and now the flag is scattered across the universe.
>
> Can you be the hero that saves the world?
## Solution
All we get is the following binary:
```console
┌──(user@kali)-[/media/sf_CTFs/checkpoint/Endgame]
└─$ xxd -g 1 flag... | sec-knowleage |
tcpreplay
===
将PCAP包重新发送,用于性能或者功能测试
## 补充说明
简单的说, **tcpreplay** 是一种pcap包的重放工具,它可以将用ethreal、wireshark工具抓下来的包原样或经过任意修改后重放回去。它允许你对报文做任意的修改(主要是指对2层、3层、4层报文头),指定重放报文的速度等,这样tcpreplay就可以用来复现抓包的情景以定位bug,以极快的速度重放从而实现压力测试。
### 选项
```shell
-A "<args>" 在使用 tcpdump 风格打印输出信息时,同时再调用tcpdump中的参数, 默认已经带有“-n,-l”,所以一般看到的都是ip地址,而没有主机名的打印,... | sec-knowleage |
# Baby Sponge (crypto, 297p, 27 solved)
In the challenge we get [challenge code](task.py)and the [library](CompactFIPS202.py) that is used.
It's pretty clear what is the goal:
```python
def dohash(self, msg):
return CompactFIPS202.Keccak(1552, 48, bytearray(msg), 0x06, 32)
(...)
self.dosend("first message(hex): ")
... | sec-knowleage |
# 安全系统整理
本篇整理一些安全相关的软硬件系统。
## IDS
IDS(Intrusion detection system),入侵检测设备
### 应用场景
工作在网络层,旁路部署,通过抓取和分析网络流量来发现攻击[1]
## IPS
IPS(Intrusion Prevention System),入侵预防系统;
### 应用场景
一般在网络层旁路,可以理解为**具备阻断能力的IDS**,是IDS的升级版(也有IDS检测到攻击通知阻断设备执行阻断动作的设备联动模式),可以覆盖网络层和应用层[1]
常见的场景是封禁网站(如非法网站的封禁)、篡改网页内容(运营商插广告)、阻断端口扫描和漏洞攻击(IPS),实施链路劫持的人必须控制... | sec-knowleage |
# elFinder ZIP 参数与任意命令注入(CVE-2021-32682)
elFinder是一个基于PHP、Jquery的开源文件管理系统。
在elFinder 2.1.48及以前的版本中,存在一处参数注入漏洞。攻击者可以利用这个漏洞在目标服务器上执行任意命令,即使是最小化安装的elFinder。
这个漏洞的原因除了参数注入外,还有默认情况下的未授权访问,因此我们可以对elFinder增加权限校验,避免任意用户操作服务器上的文件,进而避免被执行任意命令。当然,升级版本到2.1.49及以上也是必要的。
参考链接:
- <https://blog.sonarsource.com/elfinder-case-study-... | sec-knowleage |
---
title: Lsof
date: 2021-02-05 16:12:47
background: bg-blue-400
tags:
- port
- processes
- utility
categories:
- Linux Command
intro: |
This quick reference cheat sheet provides various for using lsof command.
plugins:
- copyCode
---
Getting Started
--------------
### Introduction
**lsof** me... | sec-knowleage |
# Redis
> shodan : "product:Redis"
> shodan : product:"Redis key-value store"
> fofa : protocol="redis"
**Redis 基础**
- [Redis](../../../../Integrated/数据库/笔记/Redis.md)
**相关文章**
- [细数 redis 的几种 getshell 方法](http://b1ue.cn/archives/318.html)
- [Redis 常见漏洞利用方法总结](https://mp.weixin.qq.com/s/JMGD-xUwu6bw9Uh7IKcl1A)
- [【创宇小课堂... | sec-knowleage |
# Nacos Authentication Bypass(CVE-2021-29441)
[中文版本(Chinese version)](README.zh-cn.md)
Nacos is a new open source project launched by Alibaba. It is a dynamic service discovery, configuration management and service management platform that makes it easier to build cloud-native applications. Committed to helping disco... | sec-knowleage |
mail
===
命令行下发送和接收电子邮件
## 补充说明
**mail命令** 是命令行的电子邮件发送和接收工具。操作的界面不像elm或pine那么容易使用,但功能非常完整。
### 语法
```shell
mail(选项)(参数)
```
### 选项
```shell
-b<地址>:指定密件副本的收信人地址;
-c<地址>:指定副本的收信人地址;
-f<邮件文件>:读取指定邮件文件中的邮件;
-i:不显示终端发出的信息;
-I:使用互动模式;
-n:程序使用时,不使用mail.rc文件中的设置;
-N:阅读邮件时,不显示邮件的标题;
-s<邮件主题>:指定邮件的主题;
-u<用户帐号>:读取指定用户的邮件;
-v:执行时... | sec-knowleage |
# Leetcode 题解 - 排序
<!-- GFM-TOC -->
* [Leetcode 题解 - 排序](#leetcode-题解---排序)
* [快速选择](#快速选择)
* [堆](#堆)
* [1. Kth Element](#1-kth-element)
* [桶排序](#桶排序)
* [1. 出现频率最多的 k 个元素](#1-出现频率最多的-k-个元素)
* [2. 按照字符出现次数对字符串排序](#2-按照字符出现次数对字符串排序)
* [荷兰国旗问题](#荷兰国旗问题)
* [1. 按颜色进行排序](#1-按颜色... | sec-knowleage |
#2022移动安全事记
时间线
- 0x00
- 1.2 [Kimsuky组织针对韩国新闻行业的钓鱼活动分析](https://www.freebuf.com/articles/paper/318041.html)
- 1.3 [Detecting Evasive Malware on IoT Devices Using Electromagnetic Emanations](https://thehackernews.com/2022/01/detecting-evasive-malware-on-iot.html)
- 1.3 [ThinkPHP5反序列化利用链总结与分析](https://www.fre... | sec-knowleage |
.TH Button 3tk "tcllib - BWidget"
.SH NAME
.B Button - 有增强选项的按钮组件
.SH 创建 CREATION
.B Button pathName ?option value...?
.SH 描述 DESCRIPTION
Button 组件向 Tk 按钮组件扩展了新选项。增加了动态帮助
(\fIDynamicHelp\fR) 选项,一个新面型(relief)式样,arm/disarm 回调,和
repeatdelay/repeatinterval 选项。
.SH 组件特有选项 WIDGET-SPECIFIC OPTIONS
.TP
-armcommand
指定当在 Button ... | sec-knowleage |
'\"
'\" Copyright (c) 1993 The Regents of the University of California.
'\" Copyright (c) 1994-1996 Sun Microsystems, Inc.
'\"
'\" See the file "license.terms" for information on usage and redistribution
'\" of this file, and for a DISCLAIMER OF ALL WARRANTIES.
'\"
'\" RCS: @(#) $Id: time.n,v 1.2 2003/11/24 05:10:00 b... | sec-knowleage |
# PHP代码审计
---
**环境搭建**
推荐用 phpstudy 搭建 php 代码审计的环境,简单快捷,切换 php 版本也很方便,再配置好 Xdebug 在 PHPstorm 即可远程调试。
- 下载地址: https://www.xp.cn/download.html
相关文章
- [PHP代码审计_搭建及其环境配置](https://www.modb.pro/db/184384)
如果是云服务器,推荐使用 aapanel 部署 lnmp 环境,很方便
**相关工具**
- [LoRexxar/Kunlun-M](https://github.com/LoRexxar/Kunlun-M)
```bash
... | sec-knowleage |
# Insecure Deserialization
> Serialization is the process of turning some object into a data format that can be restored later. People often serialize objects in order to save them to storage, or to send as part of communications. Deserialization is the reverse of that process -- taking data structured from some format... | sec-knowleage |
# Bottleneck
> https://download.vulnhub.com/bottleneck/Bottleneck.ova
靶场IP:`192.168.32.16`
扫描对外端口服务
```
┌──(root㉿kali)-[~]
└─# nmap -sV -p1-65535 192.168.32.16
Starting Nmap 7.92 ( https://nmap.org ) at 2022-09-11 11:33 EDT
Nmap scan report for 192.168.32.16
Host is up (0.00011s latency).
Not shown: 65533 closed tcp p... | sec-knowleage |
# Novosibirsk - Chemical plant
Category: Web
## Description
> "You must wonder why we have summoned you, AGENT? It has come to our attention that something terrible is about to take place. There is still time to prevent the disaster, and we could not think of anyone more suited for this task than you. We believe that i... | sec-knowleage |
### 软件逆向工程定义
> Reverse engineering, also called back engineering, is the process by which a man-made object is deconstructed to reveal its designs, architecture, or to extract knowledge from the object; ------ from [wikipedia](https://en.wikipedia.org/wiki/Reverse_engineering)
软件代码逆向主要指对软件的结构,流程,算法,代码等进行逆向拆解和分析。... | sec-knowleage |
## quite quixotic quest (Reversing, 300 points, 40 solves)
Well yes, it certainly is quite quixotic. (Yes, the flag format is PCTF{} )
In this task, we had a modified `curl` binary. We were able to notice the main difference
with the original binary even without binary diffing - it was enough to run `qqq --help`
to no... | sec-knowleage |
'\"
'\" Copyright (c) 1993 The Regents of the University of California.
'\" Copyright (c) 1994-1996 Sun Microsystems, Inc.
'\"
'\" See the file "license.terms" for information on usage and redistribution
'\" of this file, and for a DISCLAIMER OF ALL WARRANTIES.
'\"
'\" RCS: @(#) $Id: exec.n,v 1.2 2003/11/24 05:09:59 b... | sec-knowleage |
## SecCoding 2 (Misc, 300p)
> You should fix vulnerabilities of the given source code, WITHOUT changing its normal behaviour. Link
###ENG
[PL](#pl-version)
We are given following code, and are tasked with repairing bugs and vulnerabilities in it:
```cpp
#include <math.h>
#include <stdio.h>
#include <windows.h>
int ma... | sec-knowleage |
# assembly-3
Reversing, 400 points
## Description:
> What does asm3(0xb3fb1998,0xfe1a474d,0xd5373fd4) return? Submit the flag as a hexadecimal value (starting with '0x').
```assembly
.intel_syntax noprefix
.bits 32
.global asm3
asm3:
push ebp
mov ebp,esp
mov eax,0x62
xor al,al
mov ah,BYTE PTR [ebp+0xa]
sal... | sec-knowleage |
# leap-frog
Binary Exploitation, 300 points
## Description:
> Can you jump your way to win in the following program and get the flag?
```c
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <unistd.h>
#include <sys/types.h>
#include <stdbool.h>
#define FLAG_SIZE 64
bool win1 = false;
bool win2 = false;... | sec-knowleage |
**注:**请多喝点热水或者凉白开,可预防**肾结石,通风**等。
痛风可伴发肥胖症、高血压病、糖尿病、脂代谢紊乱等多种代谢性疾病。
### Cmstp简介:
Cmstp安装或删除“连接管理器”服务配置文件。如果不含可选参数的情况下使用,则 cmstp 会使用对应于操作系统和用户的权限的默认设置来安装服务配置文件。
微软官方文档:
https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/cmstp
**说明:**Cmstp.exe所在路径已被系统添加PATH环境变量中,因此,Cmstp命令可识别,需注意x86,x64位的Cms... | sec-knowleage |
## 红方人员实战手册
### 声明
```
Author : By klion
Date : 2020.2.15
寄语 : 愿 2020 后面的每一天都能一切安好
```
### 分享初衷
```
一来, 旨在为 "攻击" / "防御"方 提供更加全面实用的参考
还是那句老闲话 "未知攻焉知防", 所有单纯去说 "攻" 或者 "防" 的都是耍流氓, 攻守兼备才能把路越走越宽
二来, 也是为秉承共享协作, 希望能为 红队 及 部分实战攻防研究人员 做出自己应有的贡献
个人一直坚信, 真正的价值来源于实实在在的奉献,与其天天到处嘴炮,不如静下心来多反思下自己,好好踏踏实实做些对大家都有益的事
```
### 丑话说在前面
`... | sec-knowleage |

- [Grabbing OAuth Token via redirect_uri](#grabbing-oauth-token-via-redirect---uri)
- [Executing XSS via redirect_uri](#executing-xss-via-redirect---uri)
- [OAuth private key disclosure](#oauth-private-key-disclo... | sec-knowleage |
version: '2'
services:
jboss:
image: vulhub/jboss:as-6.1.0
ports:
- "9990:9990"
- "8080:8080" | sec-knowleage |
# Made by baby (for, 141p, 29 solved)
This was a very nice, and not so trivial crypto challenge.
In the end it turned out very simple, but nothing really suggested that, so we did a bit of an overkill here.
In the challenge we get [encryption code](babymade.py) and [encrypted flag](flag.enc) to work with.
We can see th... | sec-knowleage |
# Translation As A Service
* Category: Web Application
* 750 Points
* Solved by the JCTF Team
## Description
> Moving from one language to another can be rather difficult. Translation As A Service is a system that will allow you to smoothly use our own custom and unique translation algorithm, to transition from your ow... | sec-knowleage |
#!/usr/bin/env python
import sys
import os
import socket
import pickle
import base64
import marshal
import types
import inspect
import encodings.string_escape
class Flag(object):
def __init__(self):
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.connect(("172.17.0.1", 1234))
self.... | sec-knowleage |
version: '2'
services:
activemq:
image: vulhub/activemq:5.11.1-with-cron
ports:
- "61616:61616"
- "8161:8161" | sec-knowleage |
---
title: Figma
date: 2022-11-23 16:23:31.706507
background: bg-[#935aee]
label:
tags:
-
-
categories:
- Keyboard Shortcuts
intro: |
A visual cheat-sheet for the 119 keyboard shortcuts found in Figma
---
Keyboard Shortcuts
------------------
### Essential
Shortcut | Action
---|---
`Ctrl` `\` | Sho... | sec-knowleage |
.\" DO NOT MODIFY THIS FILE! It was generated by help2man 1.48.5.
.\"*******************************************************************
.\"
.\" This file was generated with po4a. Translate the source file.
.\"
.\"*******************************************************************
.TH BASENAME 1 2022年9月 "GNU coreutils... | sec-knowleage |
# misc 04
We're given a huge binary file `kevin_mitnick.raw`. Let's see what we can find out.
```
$ file kevin_mitnick.raw
kevin_mitnick.raw: data
$ ls -lah kevin_mitnick.raw
-rw-r--r-- 1 chivay chivay 2.0G Jan 4 18:21 kevin_mitnick.raw
```
Well, nothing interesting. Could be a disk image or a VM memory dump.
Time f... | sec-knowleage |
### 在内存中直接搜索 flag方法介绍
**Initial RAM disk**(`initrd`)提供了在 boot loader 阶段载入一个 RAM disk 并挂载为根文件系统的能力,从而在该阶段运行一些用户态程序,在完成该阶段工作之后才是挂载真正的根文件系统。
initrd 文件系统镜像通常为 gzip 格式,在启动阶段由 boot loader 将其路径传给 kernel,自 2.6 版本后出现了使用 cpio 格式的initramfs,从而无需挂载便能展开为一个文件系统。
initrd/initramfs 的特点便是**文件系统中的所有内容都会被读取到内存当中**,而大部分 CTF 中的 kernel pwn 题目... | sec-knowleage |
# T1098-win-账户操作
## 来自ATT&CK的描述
帐户操作可以帮助攻击者维持在环境中对凭据和某些权限级别的访问。账户操作可能包括修改权限,修改凭据,添加或更改权限组,修改帐户设置或修改执行身份验证等方式。为了创建或操纵帐户,攻击者必须已经对系统或域具有足够的权限。
## 测试案例
使用windows系统自身的一些安全进程(CMD/Powershell等)来执行这些操作,也可以利用一些经典的工具来进行账户操作(mimikatz等)。前提是你已经对系统或者域具有足够的权限。
## 检测日志
windows 安全日志
## 测试复现
```dos
C:\Windows\system32>net user test321 Te... | sec-knowleage |
.\" DO NOT MODIFY THIS FILE! It was generated by help2man 1.48.5.
.\"*******************************************************************
.\"
.\" This file was generated with po4a. Translate the source file.
.\"
.\"*******************************************************************
.TH USERS 1 2022年9月 "GNU coreutils 9.... | sec-knowleage |
##Kick Tort Teen (Forensics, 50p)
Anagram, anyone?
[Download](data.xls)
###ENG
[PL](#pl-version)
We start by converting the xls file to csv. Then we load up the values into a python script that counts the number occurences:
```python
occurences = []
for i in range(1000):
occurences.append(0)
for y in data:
for x in ... | sec-knowleage |
# T1588-001-获取能力-恶意软件
## 来自ATT&CK的描述
攻击者可能会购买、窃取或下载可在攻击目标过程使用的恶意软件。恶意软件可能包括有效载荷、植入程序、后渗透工具、后门程序、加壳程序和C2协议。攻击者可能会获取恶意软件来支持他们的行动,获得一种维持对远程机器的控制、逃避防御和攻陷后行为的手段。
除了从互联网上下载免费的恶意软件外,攻击者还可能从第三方实体购买这些恶意软件。第三方实体可以包括专门从事恶意软件开发的技术公司、犯罪市场(包括恶意软件即服务,或称MaaS),或来自个人。除了购买恶意软件外,攻击者还可能从第三方实体(包括其他攻击者)窃取和重新使用恶意软件。
## 测试案例
暂无
## 检测日志
无法有效监测
... | sec-knowleage |
# md5(coll)
* Category: Misc.
* 200 Points
* Solved by the JCTF Team
## Description
> A picture is worth a thousand words, and a flag too.
```python
from socket import timeout
from tkinter.tix import TEXT
from flask import Flask, jsonify, make_response, request, render_template, url_for
import os
import sys
import io
i... | sec-knowleage |
# saltfish
Web
## Description:
> "I have been told that the best crackers in the world can do this under 60 minutes but unfortunately I need someone who can do this under 60 seconds." - Gabriel
## Solution:
The contents of the website is:
```php
<?php
require_once('flag.php');
if ($_ = @$_GET['pass']) {
$ua = $... | sec-knowleage |
# T1071-001-应用层协议-网络协议
## 来自ATT&CK描述
攻击者可以使用与Web流量相关的应用层协议进行通信,通过与现有流量混合来进行逃避检测或网络过滤。远程系统的命令,通常是这些命令的结果,将嵌入客户端和服务器之间的协议流量中。
承载Web流量的HTTP和HTTPS等协议在环境中可能非常常见。HTTP/S数据包有许多可以隐藏数据的字段和标头。攻击者可能滥用这些协议与受害网络中受其控制的系统进行通信,同时模仿正常的预期流量。
## 测试案例
最简单的案例就是哥斯拉webshell管理工具、冰蝎webshell管理工具等
## 检测日志
network
## 测试复现
参考以下章节:[[2020-04-18-Threa... | sec-knowleage |
# NtGlobalFlag
## 关于NtGlobalFlag
在32位机器上, `NtGlobalFlag`字段位于`PEB`(进程环境块)`0x68`的偏移处, 64位机器则是在偏移`0xBC`位置. 该字段的默认值为0. 当调试器正在运行时, 该字段会被设置为一个特定的值. 尽管该值并不能十分可信地表明某个调试器真的有在运行, 但该字段常出于该目的而被使用.
该字段包含有一系列的标志位. 由调试器创建的进程会设置以下标志位:
```c
FLG_HEAP_ENABLE_TAIL_CHECK (0x10)
FLG_HEAP_ENABLE_FREE_CHECK (0x20)
FLG_HEAP_VALIDATE_PARAMETERS... | sec-knowleage |
# Code Section
## 概述
在动态链接器创建了进程镜像,并且执行了重定位后,每一个共享目标文件都有机会去执行一些初始化的代码。所有的共享目标文件会在可执行文件获得权限之前进行初始化。
在调用目标文件 A 的初始化代码之前,会首先调用所有 A 依赖的共享目标文件的初始化代码。比如说,如果目标文件 A 依赖于另外一个目标文件 B,那么 B 就会在 A 的依赖列表中,这会被记录在动态结构的 DT_NEEDED 中。循环依赖的初始化是未被定义的。
目标文件的初始化通过递归每一个被依赖的表项来完成。只有当一个目标文件依赖的所有的目标文件都处理完自己的依赖后,这个目标文件才会执行初始化代码。
下面的例子解释了两种正确的可以用来生成... | sec-knowleage |
# DIY键盘嵌入指纹识别模块实验记录
> 文章作者 [Sarah-Briggs](https://github.com/Sarah-Briggs) & [Atomic-Crash](https://github.com/Atomic-Crash) & [r0fus0d](https://github.com/No-Github)
---
## 免责声明
`本文档仅供学习和研究使用,请勿使用文中的技术源码用于非法用途,任何人造成的任何负面影响,与本人无关.`
---
下面是原作者的文章链接
- https://www.ednchina.com/news/201906211001.html 感兴趣的朋友可以先看一下原帖,然后再看这篇文... | sec-knowleage |
# Journey to the Center of the File
Grab Bag, 100 points
## Description:
> W(e( (h(a(v(e( (t(o( (g(o( (d(e(e(p(e(r)))))))))))))))))))
A file was attached.
## Solution:
Let's inspect the file:
```console
# file flag
flag: bzip2 compressed data, block size = 400k
```
Extract it and inspect the output:
```console
root@kal... | sec-knowleage |
# 安全开发 - 方案笔记
### Android 0day漏洞检测沙箱系统的设计与实现
来自2019看雪安全开发者峰会
> Android 0day漏洞检测沙箱系统的设计与实现——Moony Li of TrendMicro
### 实现思路
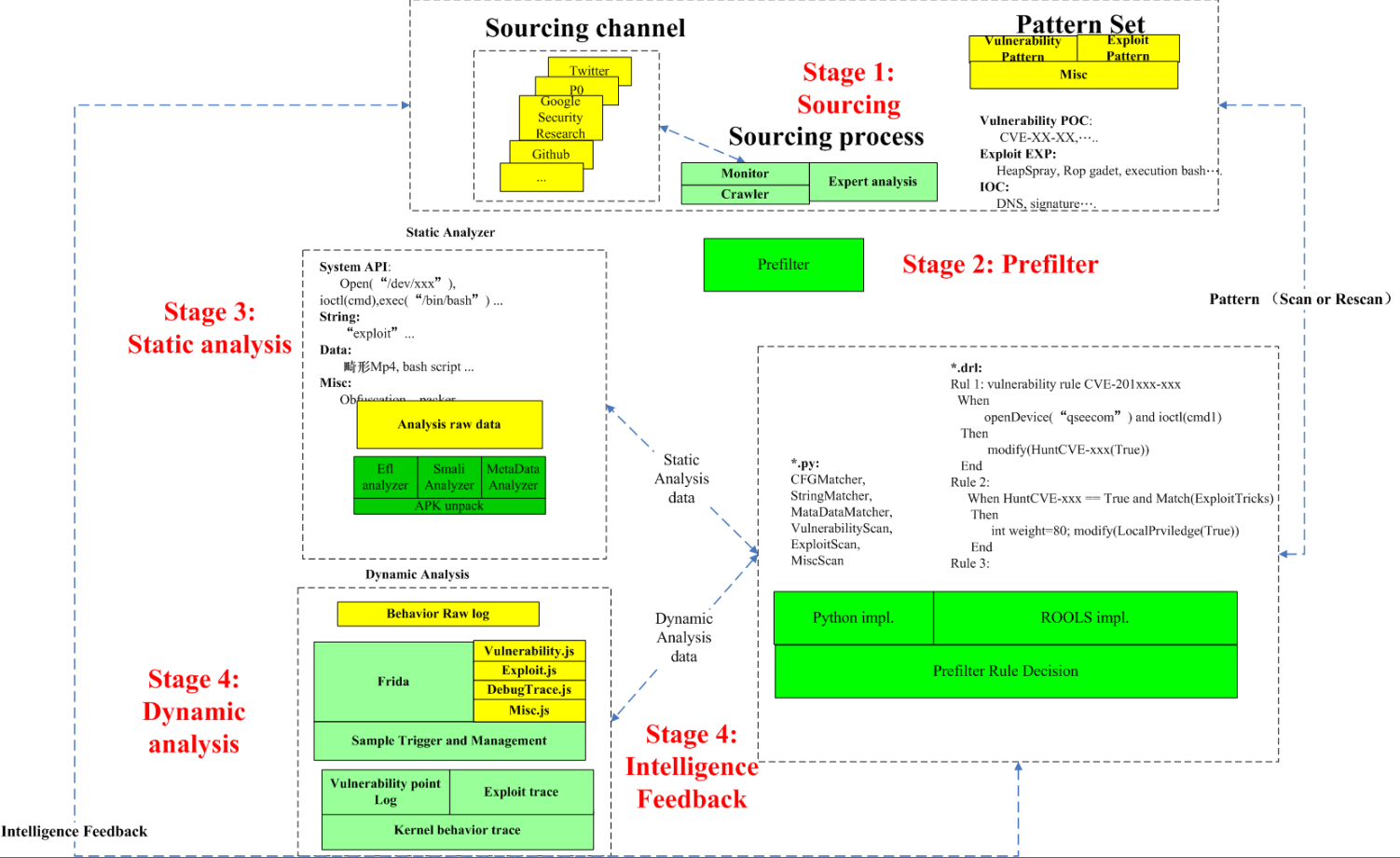
图: 总体实现思路
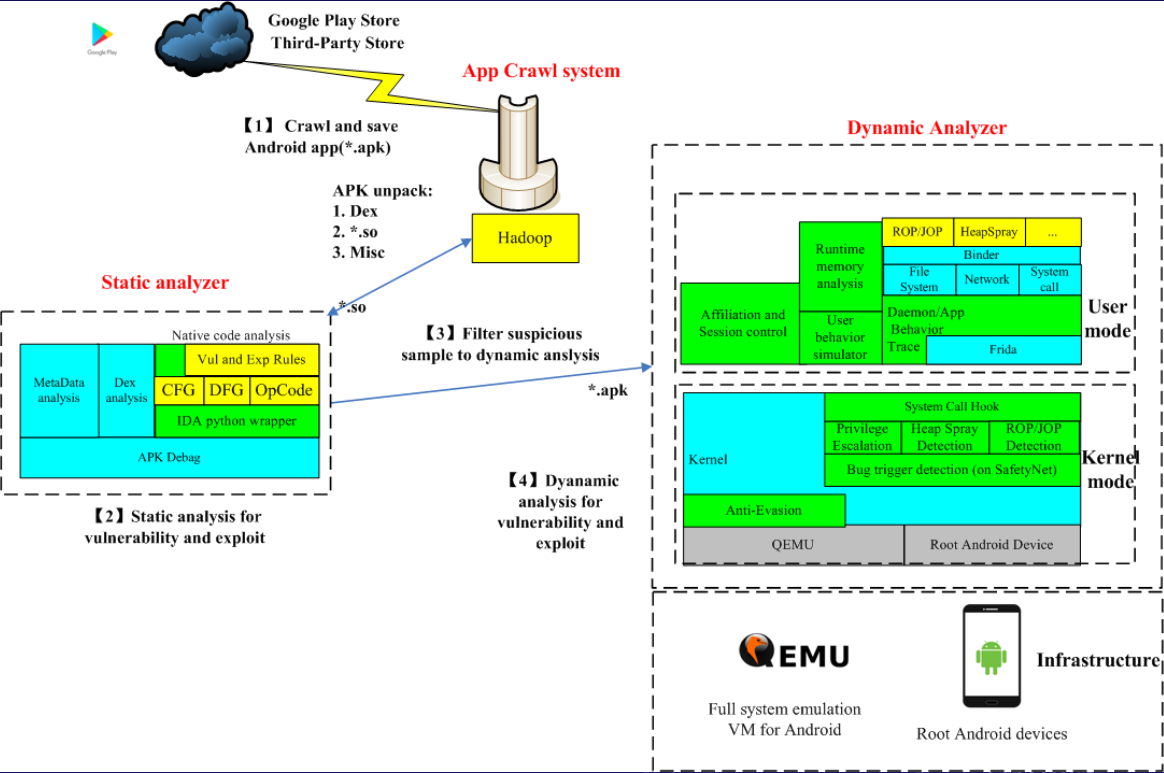
图:内部视角 | sec-knowleage |
# ZooKeeper未授权访问漏洞
## 漏洞描述
ZooKeeper默认开启在2181端口,在未进行任何访问控制情况下,攻击者可通过执行envi命令获得系统大量的敏感信息,包括系统名称、Java环境。
## 环境搭建
Zookeeper的默认开放端口是2181
```bash
wget https://archive.apache.org/dist/zookeeper/zookeeper-3.4.10/zookeeper-3.4.10.tar.gz
tar -zxvf zookeepre-3.4.10.tar.gz
cd zookeeper-3.4.10/
cd conf/
vi zoo.cfg
### 配置单机模式
tickT... | sec-knowleage |
# SQL 语法
<!-- GFM-TOC -->
* [SQL 语法](#sql-语法)
* [一、基础](#一基础)
* [二、创建表](#二创建表)
* [三、修改表](#三修改表)
* [四、插入](#四插入)
* [五、更新](#五更新)
* [六、删除](#六删除)
* [七、查询](#七查询)
* [DISTINCT](#distinct)
* [LIMIT](#limit)
* [八、排序](#八排序)
* [九、过滤](#九过滤)
* [十、通配符](#十通配符)
* [十一、计算字段](#十一计... | sec-knowleage |
# T1218-005-win-基于白名单Mshta.exe执行payload
## 来自ATT&CK的描述
Mshta.exe是一个执行微软HTA(HTML应用)的实用程序。HTA文件扩展名为.hta。HTA是独立的应用,使用与InternetExplorer相同的模型和技术来执行,但在浏览器之外执行。
攻击者可能会使用mshta.exe通过受信任的Windows实用程序来代理执行恶意.hta文件和Javascript或VBScript。已知攻击者在最初攻击阶段利用mshta.exe来执行代码的几个例子。
Mshta.exe可通过内联脚本来执行文件:mshtavbscript:Close(Execute("GetObject(""... | sec-knowleage |
package com.vulhub.authzvuln;
import org.springframework.stereotype.Controller;
import org.springframework.web.bind.annotation.GetMapping;
@Controller
public class DemoController {
@GetMapping("/admin/*")
public String Admin(){
return "admin";
}
@GetMapping("/")
public String User(){
... | sec-knowleage |
# T1078-003-win-账户登录失败
## 来自ATT&CK的描述
攻击者可能会使用凭据访问技术窃取特定用户或服务账号的凭据,或者在早期通过社会工程获得凭据,用于获得首次访问权限。
攻击者可以使用三种账号:默认账号、本地账号和域账号。默认账号是操作系统的内置账号,例如Windows系统上的访客或管理员账号,或者其他类型系统、软件或设备上的默认提供商账号。本地账号是组织配置给用户、远程支持或服务的账号,或单个系统或服务的管理账号。域账号是AD-DS(活动目录域服务)管理的账号,其访问和权限在域内不同系统和服务之间配置。域账号可以涵盖用户、管理员和服务。
攻击者可能会获取并滥用本地帐户的凭据,用于获取初始访问权限,持久性,权限提... | sec-knowleage |
# BloodHound
---
## 免责声明
`本文档仅供学习和研究使用,请勿使用文中的技术源码用于非法用途,任何人造成的任何负面影响,与本人无关.`
---
**简介**
BloodHound 可以在域内导出相关信息,将采集的数据导人本地 Neo4j 数据库,并进行展示和分析。
通过使用图与线的形式,展现域内所有相关用户、组、计算机、登陆信息、访问控制策略之间的关系.
**项目地址**
- https://github.com/BloodHoundAD/BloodHound
**相关文章**
- [域渗透分析工具BloodHound 1.5.2入门实战](https://www.freebuf.com/sectool/1790... | sec-knowleage |
# Grafana
## Introduction
What would you do if you came across a website that uses Grafana?
## How to Detect
Try to HTTP request to `https://example.com/login` and there is a form login
1. Find the related CVE by checking grafana version
* How to find the grafana version
Try to request to `https://example.com/login` an... | sec-knowleage |
version: '2'
services:
admin:
image: vulhub/xxl-job:2.2.0-admin
depends_on:
- db
ports:
- "8080:8080"
executor:
image: vulhub/xxl-job:2.2.0-executor
depends_on:
- admin
ports:
- "9999:9999"
db:
image: mysql:5.7
environment:
- MYSQL_ROOT_PASSWORD=root | sec-knowleage |
# XSS (re, 6 solves, 900p)
> The flag format is MeePwnCTF{correct_input}
> Unzip password: MeePwn
Here's the main function:

If the program is ran without any arguments (and thus argc==1), it spawns 2 additional processess with args `1` and `1 2`, and goes on to execute `argc_switch`:
![argc_switch... | sec-knowleage |
这次继续围绕第一篇,第一季关于后门:
https://micropoor.blogspot.hk/2017/12/php.html
做整理与补充。在深入一步细化demo notepad++。
后门是渗透测试的分水岭,它分别体现了攻击者对目标机器的熟知程度,环境,编程语言,了解对方客户,以及安全公司的本质概念。这样的后门才能更隐蔽,更长久。
而对于防御者需要掌握后门的基本查杀,与高难度查杀,了解被入侵环境,目标机器。以及后门或者病毒可隐藏角落,或样本取证,内存取证。
所以说后门的安装与反安装是一场考试,一场实战考试。
这里要引用几个概念,只有概念清晰,才能把后门加入概念化,使其更隐蔽。
**1:攻击方与防御方的本质是什么?**
增... | sec-knowleage |
# 考证经验分享
## 简介
OSCP (Offensive Security Certified Professional) 是 Offensive Security 公司提供的一种专业的网络渗透测试证书。它是一项实践性强、高度挑战性的证书,需要考生通过一个 24 小时的实际渗透测试考试来获得。考试中,考生需要在给定的时间内完成对不同系统的渗透测试,并在线提交渗透报告。
通过 OSCP 证书的考生需要具备较高的网络安全知识和实践经验,能够独立进行网络渗透测试并生成详细的渗透报告。该证书可以作为网络安全专业人员的资格证明,并可以为考生在职业发展中提供帮助。
## 考试结构
- 考试有三台独立考试靶机和一套域环境(三台机器)
- 三台... | sec-knowleage |
Subsets and Splits
Top 100 EPUB Books
This query retrieves a limited set of raw data entries that belong to the 'epub_books' category, offering only basic filtering without deeper insights.