text stringlengths 100 9.93M | category stringclasses 11
values |
|---|---|
# DaaS (crypto 50)
###ENG
[PL](#pl-version)
In the task we get the address of the remote service and the [source code](DaaS.py).
We also get a file with RSA-encrypted flag.
```
flag = 0xc18b1d3b892e29863d8a6b46059995173635a3fd9f2ad877143a2d14ee736d8b12f9e735d6877a553312101eb757a0e3b3795bea88f2b4f72d1eb47ef6062a0dfd6598... | sec-knowleage |
---
title: Quip.com
date: 2022-11-23 16:23:31.697261
background: bg-[#e4795b]
label:
tags:
-
-
categories:
- Keyboard Shortcuts
intro: |
A visual cheat-sheet for the 52 keyboard shortcuts found in Quip
---
Keyboard Shortcuts
------------------
### Anywhere
Shortcut | Action
---|---
<code>\`</code> |... | sec-knowleage |
modetest
===
DRM/KMS驱动程序libdrm中的模式测试工具
## 补充说明
`modetest` 是一个用于测试和验证 DRM(Direct Rendering Manager)驱动程序功能的命令行工具。
### 安装
- **源码**:[Mesa / drm · GitLab](https://gitlab.freedesktop.org/mesa/drm)
- **下载**:[Index of /libdrm (dri.freedesktop.org)](https://dri.freedesktop.org/libdrm/)
__编译__
```shell
./configure --prefix=/opt/... | sec-knowleage |
## AdobeReader 逻辑漏洞(CVE-2021-21037)
> 360漏洞研究院 王志远 发布于 2022-08-17 03:17
### 漏洞描述
Acrobat Reader DC 版本 2020.013.20074(及更早)、2020.001.30018(及更早)和 2017.011.30188(及更早)受路径遍历漏洞影响。未经身份验证的攻击者可以利用此漏洞在当前用户设备中执行任意代码。
### 影响范围
Acrobat Reader DC versions versions 2020.013.20074 (and earlier), 2020.001.30018 (and earlier) and 2017.01... | sec-knowleage |
# BSidesSF CTF 2018
Team: shalom, nazywam, chivay
### Table of contents
* [Rotaluklak (pwn)](pwn_rotaluklak) | sec-knowleage |
# Job Portal (200, Web/Exploit)
> They pretend to check your letter of application.
> I want to proof that they are doing nothing to help you. Get me access to the filesystem!
In this task we were given access to service allowing to upload tar files. When uploaded, we could check the
tarball contents (file names only)... | sec-knowleage |
# A Simple Question
Web Exploitation, 650 points
## Description:
> There is a website running at http://2018shell3.picoctf.com:15987 (link). Try to see if you can answer its question.
## Solution:
We are presented with a web form which contains a single question: "What is the answer?".
If we attempt to provide an arb... | sec-knowleage |
# Exchange 搭建
---
**实验环境组成**
- VMware
- 一台 win2016 ,域控(为了你的身心健康着想,不要使用其他版本的 windows server 系统)
---
## 邮件服务器角色
在 exchange 2010 中,exchange 包含五个服务器角色,分别为邮箱服务器,客户端访问服务器,集线传输服务器,统一消息服务器,边缘传输服务器。
exchange 2013 中服务器为 3 个:邮箱服务器,客户端访问服务器,边缘传输服务器
exchange 2016 和 2019 中只有邮箱服务器和边缘传输服务器
---
## 接口和协议
**OWA**
owa 即 outlook web app, 即... | sec-knowleage |
# MacOS 的安全和隐私指南
> * 原文地址:[macOS Security and Privacy Guide](https://github.com/drduh/macOS-Security-and-Privacy-Guide)
> * 原文作者:[drduh](https://github.com/drduh)
> * 译文出自:[掘金翻译计划](https://github.com/xitu/gold-miner)
> * 译者:[Nicolas(Yifei) Li](https://github.com/yifili09), [MAYDAY1993](https://github.com/MAYDAY1993), [... | sec-knowleage |
#!/usr/bin/env python
import sys
from deadpool_dca import *
def processinput(iblock, blocksize):
p='%0*x' % (2*blocksize, iblock)
f=open("/tmp/xd", "wb")
f.write(p.decode("hex"))
f.close()
return ["--stdin </tmp/xd"]
def processoutput(output, blocksize):
o=output.replace(" ","")
return in... | sec-knowleage |
cut
===
连接文件并打印到标准输出设备上
## 补充说明
**cut 命令** 用来显示行中的指定部分,删除文件中指定字段。cut 经常用来显示文件的内容,类似于 type 命令。
说明:该命令有两项功能,其一是用来显示文件的内容,它依次读取由参数 file 所指 明的文件,将它们的内容输出到标准输出上;其二是连接两个或多个文件,如`cut fl f2 > f3`将把文件 fl 和 f2 的内容合并起来,然后通过输出重定向符“>”的作用,将它们放入文件 f3 中。
当文件较大时,文本在屏幕上迅速闪过(滚屏),用户往往看不清所显示的内容。因此,一般用 more 等命令分屏显示。为了控制滚屏,可以按 Ctrl+S 键,停止滚屏;按... | sec-knowleage |
version: '2'
services:
flask:
build: .
command: -w 4 -b :8000 -u www-data -g www-data --access-logfile - app:app
volumes:
- .:/app
ports:
- "8000:8000" | sec-knowleage |
source
===
在当前Shell环境中从指定文件读取和执行命令。
### 概要
source filename [arguments]
### 主要用途
- 执行文件并从文件中加载变量及函数到执行环境
#### 参数
filename:要执行的文件
arguments(可选):传递给文件的参数
#### 返回值
source返回文件最后一个命令的返回值,如果文件不能读取则会失败
#### 错误用法
- 文件在`$PATH`中找不到。
- 文件未给出。
### 例子
- 在一些工具的执行过程中,会把环境变量设置以"export XXX=XXXXXX"或"declare XXX=XXXXXX"的形式导出到
一个文件中,然后用sou... | sec-knowleage |
whereis
===
查找二进制程序、代码等相关文件路径
## 补充说明
**whereis命令** 用来定位指令的二进制程序、源代码文件和man手册页等相关文件的路径。
whereis命令只能用于程序名的搜索,而且只搜索二进制文件(参数-b)、man说明文件(参数-m)和源代码文件(参数-s)。如果省略参数,则返回所有信息。
和find相比,whereis查找的速度非常快,这是因为linux系统会将 系统内的所有文件都记录在一个数据库文件中,当使用whereis和下面即将介绍的locate时,会从数据库中查找数据,而不是像find命令那样,通 过遍历硬盘来查找,效率自然会很高。 但是该数据库文件并不是实时更新,默认情况下时一星期... | sec-knowleage |
# XXE
## SAX
> Java SAX(Simple API for XML)库是一种处理XML(eXtensible Markup Language)文档的标准Java API。SAX库是一种事件驱动的XML解析器,它使用基于事件的回调机制来解析XML文档。在解析过程中,SAX解析器会将XML文档中的每个元素解析成一个事件,并在解析到每个事件时触发相应的回调方法。
>
> 下面是SAX库的一些详细说明:
>
> 1. SAX库是基于Java的标准API,因此它可以与任何Java程序一起使用。
> 2. SAX库提供了一个处理XML文档的API,可以让开发者从XML文档中获取数据并进行处理。
> 3. SAX库是一种轻量级的... | sec-knowleage |
**Authors**: < [nixawk](https://github.com/nixawk) >
----
## Android Hacking and Security
1. [exploiting securing application components](http://resources.infosecinstitute.com/android-hacking-security-part-1-exploiting-securing-application-components/)
2. [content provider leakage](http://resources.infosecinstitute.com... | sec-knowleage |
# Bypass Two-Factor Authentication
1. Response manipulation
The response is
```
HTTP/1.1 404 Not Found
...
{"code": false}
```
Try this to bypass
```
HTTP/1.1 404 Not Found
...
{"code": true}
```
2. Status code manipulation
The response is
```
HTTP/1.1 404 Not Found
...
{"code": false}
```
Try this to bypass
```
HTTP/1... | sec-knowleage |
# shabaKernel
Category: Reversing, 350 points
## Description
> This binary is not an elf. So what is it?
>
> Load the .ko file and find out...
>
> Use the image:
>
> http://uec-images.ubuntu.com/releases/focal/release-20201210/
>
> Good luck!
Two binary files were attached.
## Solution:
Let's check the binary files... | sec-knowleage |
# Jackson-databind 反序列化漏洞(CVE-2017-7525)
Jackson-databind 支持 [Polymorphic Deserialization](https://github.com/FasterXML/jackson-docs/wiki/JacksonPolymorphicDeserialization) 特性(默认情况下不开启),当 json 字符串转换的 Target class 中有 polymorph fields,即字段类型为接口、抽象类或 Object 类型时,攻击者可以通过在 json 字符串中指定变量的具体类型 (子类或接口实现类),来实现实例化指定的类,借助某些特殊的 cla... | sec-knowleage |
# BugDB v3 - FLAG0
## 0x00 Overview
Pretty much same as [BugDB v1][1] and [v2][2]. But this one also need to combine with arbitary file reading.
## 0x01 Take a Tour
### query
There is attachments available. But initially they are all empty.
```graphql
query{
user{
edges{
node{
id
username
... | sec-knowleage |
# Static Scripting
Category: Steganography
## Description
> Who doesn't like to watch some static noise?
>
> Hint: The video duration is not random
A video was attached.
## Solution
Attached was a video of 24:00 minutes where each frame looked like a collection of random colorful pixels such as:
 1991 Free Software Foundation
.\" See section COPYING for conditions for redistribution
.TH size 1 "5 November 1991" "cygnus support" "GNU Development Tools"
.de BP
.sp
.ti \-.2i
\(**
..
.SH NAME
size \- 列出段节大小和总共大小
.SH "总览 (SYNOPSIS)"
.hy 0
.na
.TP
.B size
.RB "[\|" \-A \||\| \-B \||\| \c
.BI "\-\-fo... | sec-knowleage |
# Bettercap
**************
## Bettercap包描述
**************
Bettercap是一款适用于网络攻击和监控的瑞士军刀。这是一个用于网络捕获,分析和MIMT攻击的网络安全工具。
[Lynis 主页](https://www.bettercap.org/)
[Kali Bettercap仓库](https://git.kali.org/gitweb/?p=packages/bettercap.git;a=summary)
[资料来源](https://github.com/bettercap/bettercap)
作者:Bettercap dev team
许可:GPLv3
****... | sec-knowleage |
# Metasploit
## Summary
* [Installation](#installation)
* [Sessions](#sessions)
* [Background handler](#background-handler)
* [Meterpreter - Basic](#meterpreter---basic)
* [Generate a meterpreter](#generate-a-meterpreter)
* [Meterpreter Webdelivery](#meterpreter-webdelivery)
* [Get System](#get-system)
... | sec-knowleage |
lsattr
===
查看文件的第二扩展文件系统属性
## 补充说明
**lsattr命令** 用于查看文件的第二扩展文件系统属性。
### 语法
```shell
lsattr(选项)(参数)
```
### 选项
```shell
-E:可显示设备属性的当前值,但这个当前值是从用户设备数据库中获得的,而不是从设备直接获得的。
-D:显示属性的名称,属性的默认值,描述和用户是否可以修改属性值的标志。
-R:递归的操作方式;
-V:显示指令的版本信息;
-a:列出目录中的所有文件,包括隐藏文件。
```
lsattr经常使用的几个选项-D,-E,-R这三个选项不可以一起使用,它们是互斥的,经常使用的还有-l,-H,使用lsatt... | sec-knowleage |
# OFB
OFB全称为输出反馈模式(Output feedback),其反馈内容是分组加密后的内容而不是密文。
## 加密
## 解密
## 优缺点
### 优点
1. 不具有错误传播特性。
### 缺点
1. IV 无需保密,但是对每个消息必须选择不同的 IV。
2. 不具有自同步能力。
## 适用场景
适用于一些明文冗余度比较大的场景,如图像加密和语音加密。 | sec-knowleage |
.\" Copyright (c) 1996 Free Software Foundation, Inc.
.\" This program is distributed according to the Gnu General Public License.
.\" See the file COPYING in the kernel source directory
.\"
.TH MODINFO 8 "11 Nov 1997" Linux "模块支持"
.SH NAME
modinfo \- 显示当前内核模块信息
.SH 总览
.B modinfo
[ options ] <module_file>
.SH 描述
.B mod... | sec-knowleage |
---
title: Adobe Photoshop
date: 2022-11-23 16:23:31.706034
background: bg-[#071c25]
label:
tags:
-
-
categories:
- Keyboard Shortcuts
intro: |
A visual cheat-sheet for the 283 keyboard shortcuts found in Adobe Photoshop
---
Keyboard Shortcuts
------------------
### Popular shortcuts
Shortcut | Acti... | sec-knowleage |
"""Main application."""
import base64
import hashlib
import hmac
import logging
import os
import textwrap
import time
import urllib
import webapp2
from google.appengine.api import datastore_errors
from google.appengine.api import memcache
from google.appengine.ext import ndb
HANDICAP = 10 * 2
FLAG_LENGTH = 64
BAN ... | sec-knowleage |
command
===
调用并执行指定的命令
## 补充说明
**command命令** 调用指定的指令并执行,命令执行时不查询shell函数。command命令只能够执行shell内部的命令。
### 语法
```shell
command(参数)
```
### 参数
指令:需要调用的指令及参数。
### 实例
使用command命令调用执行`echo Linux`,输入如下命令:
```shell
command echo Linux #调用执行shell内部指令
```
上面的命令执行后,将调用执行命令`echo Linux`,其执行结果如下:
```shell
Linux
``` | sec-knowleage |
## Puzzleng (forensic, 150p, 24 solves)
> Next Generation of Puzzle!
> [puzzleng-edb16f6134bafb9e8b856b441480c117.tgz](puzzleng.tgz)
### PL
[ENG](#eng-version)
Z dołączonego do zadania pliku tgz wypakowujemy dwa kolejne - [encrypt](encrypt) (to binarka, elf) oraz [flag.puzzle](flag.puzzle) (nieznany typ pliku).
Łatwo ... | sec-knowleage |
# Oracle
Oracle Database Server 是美国甲骨文(Oracle)公司的一套关系数据库管理系统。该数据库管理系统提供数据管理、分布式处理等功能。
> fofa : app="Oracle-数据库"
**版本号**
- oracle 版本号是真的乱,Oracle 数据库版本号请看维基百科 [Oracle Database](https://en.wikipedia.org/wiki/Oracle_Database)
**注入**
- [Oracle数据库注入笔记](../Web安全/Web_Generic/SQLi.md#Oracle)
**Tips**
- scott 用户默认没有启用
- 可以用 orac... | sec-knowleage |
## Crypto-Pirat (Crypto, 50p)
Did the East German Secret Police see a Pirat on the sky? Help me find out!
Hint: We had 9 planets from 1930–2006...
Hint2: Each planet has a number. (There's a table on a well-known website).
After that you might be interested in ciphers used by the secret police.
[attachment](cip... | sec-knowleage |
.\" auto-generated by docbook2man-spec $Revision: 1.1 $
.TH "DROP DATABASE" "7" "2003-11-02" "SQL - Language Statements" "SQL Commands"
.SH NAME
DROP DATABASE \- 删除一个数据库
.SH SYNOPSIS
.sp
.nf
DROP DATABASE \fIname\fR
.sp
.fi
.SH "DESCRIPTION 描述"
.PP
\fBDROP DATABASE\fR 删除一个现存数据库的目录入口并且删除包含数据的目录。 只有数据库所有者能够执行这条命令(通常也是数据库... | sec-knowleage |
# 离散对数
## 基本定义
在了解离散对数时,我们先来了解几个基本定义。
**定义1**
在群 G 中,g 为 G 的生成元,也就是说群 G 中每一个元素都可以写成 $y=g^k$,我们称 k 为 y 在群 G 中的对数。
**定义2**
设 $m\geq 1$,$(a,m)=1$ ,使得 $a^d \equiv 1\pmod m$ 成立的最小正整数 d 称为 a 对模 m 的指数或者阶,我们一般将其记为 $\delta_m(a)$。
**定义3**
当 $\delta_m(a)=\varphi(m)$ 时,称 a 是模 m 的原根,简称 m 的原根。
## 一些性质
**性质1**
使得 $a^d \equiv 1\pmod m... | sec-knowleage |
.\" -*- nroff -*-
.\"
.\" Author: Tatu Ylonen <ylo@cs.hut.fi>
.\" Copyright (c) 1995 Tatu Ylonen <ylo@cs.hut.fi>, Espoo, Finland
.\" All rights reserved
.\"
.\" As far as I am concerned, the code I have written for this software
.\" can be used freely for any purpose. Any derived versions of this
.... | sec-knowleage |
# These are supported funding model platforms
github: # Replace with up to 4 GitHub Sponsors-enabled usernames e.g., [user1, user2]
patreon: # Replace with a single Patreon username
open_collective: # Replace with a single Open Collective username
ko_fi: neversec
tidelift: # Replace with a single Tidelift platform-nam... | sec-knowleage |
pvdisplay
===
显示物理卷的属性
## 补充说明
**pvdisplay命令** 用于显示物理卷的属性。pvdisplay命令显示的物理卷信息包括:物理卷名称、所属的卷组、物理卷大小、PE大小、总PE数、可用PE数、已分配的PE数和UUID。
### 语法
```shell
pvdisplay(选项)(参数)
```
### 选项
```shell
-s:以短格式输出;
-m:显示PE到LE的映射。
```
### 参数
物理卷:要显示的物理卷对应的设备文件名。
### 实例
使用pvdisplay命令显示指定的物理卷的基本信息。在命令行中输入下面的命令:
```shell
[root@localhost ~]#... | sec-knowleage |
.\" auto-generated by docbook2man-spec $Revision: 1.1 $
.TH "CREATE RULE" "7" "2003-11-02" "SQL - Language Statements" "SQL Commands"
.SH NAME
CREATE RULE \- 定义一个新的重写规则
.SH SYNOPSIS
.sp
.nf
CREATE [ OR REPLACE ] RULE \fIname\fR AS ON \fIevent\fR
TO \fItable\fR [ WHERE \fIcondition\fR ]
DO [ INSTEAD ] { NOTHING ... | sec-knowleage |
version: '2'
services:
web:
image: vulhub/confluence:6.10.2
ports:
- "8090:8090"
depends_on:
- db
db:
image: postgres:10.7-alpine
environment:
- POSTGRES_PASSWORD=postgres
- POSTGRES_DB=confluence | sec-knowleage |
# Bad Computations (Crypto, 800p)
In the task we get [crypto code](crypt.py) and encrypted flag: `hnd/goJ/e4h1foWDhYOFiIZ+f3l1e4R5iI+Gin+FhA==`
We proceed with labelling the poorly obfuscated functions.
It's quite clear we have there something like: `primes_in_range`, `prime_sieve`, `extended_gcd` and `mod_inv`.
Next w... | sec-knowleage |
/*
* Copyright 2014 the original author or authors.
*
* Licensed under the Apache License, Version 2.0 (the "License");
* you may not use this file except in compliance with the License.
* You may obtain a copy of the License at
*
* http://www.apache.org/licenses/LICENSE-2.0
*
* Unless required by applica... | sec-knowleage |
# DC5-WalkThrough
---
## 免责声明
`本文档仅供学习和研究使用,请勿使用文中的技术源码用于非法用途,任何人造成的任何负面影响,与本人无关.`
---
**靶机地址**
- https://www.vulnhub.com/entry/dc-5,314/
**Description**
DC-5 is another purposely built vulnerable lab with the intent of gaining experience in the world of penetration testing.
The plan was for DC-5 to kick it up a notch,... | sec-knowleage |
## 漏洞分析工具
|Vulnerability Analysis||||||
|:-:|:-:|:-:|:-:|:-:|:-:|
|[BBQSQL](BBQSQL.md)|[BED](BED.md)|[cisco-auditing-tool](cisco-auditing-tool.md)|[cisco-global-exploiter](cisco-global-exploiter.md)||[cisco-ocs](cisco-ocs.md)|
|[cisco-torch](cisco-torch.md)|[copy-router-config](copy-router-config,md)|DBPwAudit|[Doona](... | sec-knowleage |
ss
===
比 netstat 好用的socket统计信息,iproute2 包附带的另一个工具,允许你查询 socket 的有关统计信息
## 补充说明
**ss命令** 用来显示处于活动状态的套接字信息。ss命令可以用来获取socket统计信息,它可以显示和netstat类似的内容。但ss的优势在于它能够显示更多更详细的有关TCP和连接状态的信息,而且比netstat更快速更高效。
当服务器的socket连接数量变得非常大时,无论是使用netstat命令还是直接`cat /proc/net/tcp`,执行速度都会很慢。可能你不会有切身的感受,但请相信我,当服务器维持的连接达到上万个的时候,使用netstat等于浪费 生命,而用... | sec-knowleage |
# Robots Rule
Web, 100 points
## Description:
A website was linked to.
```html
<html>
<head>
<style>
div {text-align: center;}
img {display: block; margin-left: auto; margin-right: auto; height: 45%; width: 35%}
html {height: 100%; background: url(Background.jpg) no-repeat center center; background-size: cover; }
</... | sec-knowleage |
#!/usr/bin/env python3
import requests
import sys
from bs4 import BeautifulSoup
from urllib.parse import urljoin
import random
import logging
import time
s = requests.Session()
def get_csrf_token(html):
soup = BeautifulSoup(html)
auth_token = soup.find("input", {"name": "authenticity_token"})
return auth... | sec-knowleage |
.ig
Copyright (C) 1989-2001 Free Software Foundation, Inc.
Permission is granted to make and distribute verbatim copies of
this manual provided the copyright notice and this permission notice
are preserved on all copies.
Permission is granted to copy and distribute modified versions of this
manual under the conditions ... | sec-knowleage |
'\"
'\" Copyright (c) 1993 The Regents of the University of California.
'\" Copyright (c) 1994-1996 Sun Microsystems, Inc.
'\" Copyright (c) 2000 Scriptics Corporation.
'\"
'\" See the file "license.terms" for information on usage and redistribution
'\" of this file, and for a DISCLAIMER OF ALL WARRANTIES.
'\"
'\" RCS... | sec-knowleage |
from library import *
from lib_attack import *
import sys
import numpy as np
inputs, outputs, traces = parse(sys.argv[1], left=750000, right=800000)
normalize(traces)
smooth(traces, 25)
align(traces, range(-5000, 15000))
save_traces(sys.argv[2], inputs, outputs, traces) | sec-knowleage |
# USSH (crypto, 31 solved, 138p)
```
We've developed a new restricted shell. It also allows to manage user access more securely.
Let's try it nc crypto-01.v7frkwrfyhsjtbpfcppnu.ctfz.one 1337
```
In the task we get access to a blackbox restricted shell.
We can use command `help` to get list of available commands and th... | sec-knowleage |
# Cody's First Blog
## [Flag0](./flag0) -- Found
- What was the first input you saw?
- Figuring out what platform this is running on may give you some ideas
- Code injection usually doesn't work
## [Flag1](./flag1) -- Found
- Make sure you check everything you're provided
- Unused code can often lead to information you... | sec-knowleage |
# Public Key Infrastructure (crypto)
## ENG
[PL](#pl-version)
In the task we get [code](task.py) running on the server.
We can "register" a new user, and for given `login name` and set of binary bytes `n` we get RSA-encrypted with `(65537, n)` digital signature of string `'MSG = {n: ' + n + ', name: ' + name + '}'`.
By... | sec-knowleage |
# Request Smuggling
> HTTP Request smuggling occurs when multiple "things" process a request, but differ on how they determine where the request starts/ends. This disagreement can be used to interfere with another user's request/response or to bypass security controls. It normally occurs due to prioritising different H... | sec-knowleage |
# Inspector Gadget
Category: Web
## Description
> [YouTube Video](https://www.youtube.com/watch?v=EcF2LOaLgA0&feature=youtu.be)
## Solution
We enter the website and get a simple page with three links: "Home", "About", and "Admin". If we click "Admin", we get redirected back to the index with an error message: "*You're ... | sec-knowleage |
# 扩展维纳攻击
* `扩展维纳攻击`来自[`《Extending Wiener's Attack in the Presence of Many Decrypting Exponents》`](https://www.sci-hub.ren/https://link.springer.com/chapter/10.1007/3-540-46701-7_14),相关题目在CTF中已经出现了,例如2020羊城杯的Simple,但都是一些*模板题*,这里将详细分析原论文中提出的方法以及分析方式,写明扩展维纳攻击原理以及在文末给出了一些**开放问题**欢迎讨论。
## 原理分析
### 维纳(Wiener)的方法
* 维纳`Wiener`... | sec-knowleage |
# Postbook - FLAG4
## 0x00 Edit Post
http://127.0.0.1/1234567890/index.php?page=edit.php&id=3

## 0x01 Edit Others Post
The id seems can be change.
http://127.0.0.1/1234567890/index.php?page=edit.php&id=1

## 0x02 FLAG
Save the edit result. Get the flag.

```
### 参数
文件:指定要进行拼写检查的文件。 | sec-knowleage |
# T1053-002-win-通过GPO计划任务进行大规模的持久性和执行
## 来自ATT&CK的描述
诸如at和schtasks之类的实用程序可与Windows Task Scheduler一起使用来调度程序或脚本在某日期和时间执行。只要身份认证通过可以使用RPC,并且打开了文件和打印机共享功能,就可以在远程系统上调度任务。在远程系统上调度任务通常需要远程系统管理员群组的成员执行。
攻击者可能会通过任务调度在系统启动时或在计划的基础上执行程序以实现持久性,作为横向移动的一部分进行远程执行,获得系统权限,或者在指定账号的上下文下运行进程。
## 测试案例
通过Group Policy Management Console (GPM... | sec-knowleage |
# Secrets (Forensics, 304p, 10 solved)
In the challenge we get an archive with a bunch of PNG files.
Initial analysis shows only 2 strange strings:
1. `no SecDrive`
2. base64 encoded `the password is: atalmatal`
After some extensive googling we finally found https://github.com/mgeitz/albumfs which seemed to fit our tas... | sec-knowleage |
# not crypto
Reverse Engineering, 150 points
## Description
> there's crypto in here but the challenge is not crypto... 🤔
A binary file was attached.
## Solution
Let's run the attached file:
```console
┌──(user@kali)-[/media/sf_CTFs/pico/not_crypto]
└─$ ./not-crypto
I heard you wanted to bargain for a flag... whatcha ... | sec-knowleage |
**Authors**: < [nixawk](https://github.com/nixawk) >
----
# How to gather dns information ?
- Passive mode
- DNS Enumeration
- OSINT
- Offensive mode
- spider websites
- Tools
- recon-ng
- dnsrecon
- theHarvester
## Passive mode
### DNS Enumeration
**DNS enumeration** is the process of locating all the DNS ... | sec-knowleage |
csplit
===
将一个大文件分割成小的碎片文件
## 补充说明
**csplit命令** 用于将一个大文件分割成小的碎片,并且将分割后的每个碎片保存成一个文件。碎片文件的命名类似“xx00”,“xx01”。csplit命令是split的一个变体,split只能够根据文件大小或行数来分割,但csplit能够根据文件本身特点来分割文件。
### 语法
```shell
csplit(选项)(参数)
```
### 选项
```shell
-b<输出格式>或--suffix-format=<输出格式>:预设的输出格式其文件名称为xx00,xx01等,用户可以通过改变<输出格式>来改变输出的文件名;
-f<输出字首字符串>或--p... | sec-knowleage |
# Sections
节区包含目标文件中除了 ELF 头部、程序头部表、节区头部表的所有信息。节区满足以下条件
- 每个节区都有对应的节头来描述它。但是反过来,节区头部并不一定会对应着一个节区。
- 每个节区在目标文件中是连续的,但是大小可能为 0。
- 任意两个节区不能重叠,即一个字节不能同时存在于两个节区中。
- 目标文件中可能会有闲置空间(inactive space),各种头和节不一定会覆盖到目标文件中的所有字节,**闲置区域的内容未指定**。
许多在 ELF 文件中的节都是预定义的,它们包含程序和控制信息。这些节被操作系统使用,但是对于不同的操作系统,同一节区可能会有不同的类型以及属性。
可执行文件是由链接器将一些单独的目... | sec-knowleage |
# Data
> 每个 Vue 实例都会代理其 data 对象里所有的属性,相当于 React 中的 State
### data
**注意**:data 必须是函数,这里的 data 只是一个特殊的原始属性
```js
var data = { a: 1 }
var vm = new Vue({
data: data
})
vm.a === data.a // -> true
// 设置属性也会影响到原始数据
vm.a = 2
data.a // -> 2
// ... 反之亦然
data.a = 3
vm.a // -> 3
```
注意只有这些被代理的属性是响应的,也就是说值的任何改变都是触发视图的重新渲染。如果在实例创建... | sec-knowleage |
## ltseorg (crypto, 4 points, 93 solves)
make some (charlie)hash collisions!
In this task we were given a code with function hashing strings and were asked to create
a hash collision. After reading the
algorithm, we quickly noticed that the padding function was non-standard and flawed:
```
def pad_msg(msg):
while no... | sec-knowleage |
'\"
'\" Copyright (c) 1995-1997 Sun Microsystems, Inc.
'\" Copyright (c) 1998-2000 by Ajuba Solutions.
'\"
'\" See the file "license.terms" for information on usage and redistribution
'\" of this file, and for a DISCLAIMER OF ALL WARRANTIES.
'\"
'\"
'\" The definitions below are for supplemental macros used in Tcl/Tk... | sec-knowleage |
-------------------------------------------
[Eletronics] Eletronic Ballot Box Prototype - 50 points
-------------------------------------------
> A member of Project SKY has infiltrated into a Club recycling facility and got access to one of the first prototypes of what became, afterwards, an electronic ballot box (yes... | sec-knowleage |
原文 by r00tgrok
## 0x01 WAF的常见特征
之所以要谈到WAF的常见特征,是为了更好的了解WAF的运行机制,这样就能增加几分绕过的机会了。本文不对WAF做详细介绍只谈及几点相关的。
总体来说WAF(Web Application Firewall)的具有以下四个方面的功能
1. 审计设备用来截获所有HTTP数据或者仅仅满足某些规则的会话
2. 访问控制设备用来控制对Web应用的访问,既包括主动安全模式也包括被动安全模式
3. 架构/网络设计工具,当运行在反向代理模式他们被用来分配职能,集中控制虚拟基础结构等。
4. WEB应用加固工具,这些功能增强被保护Web应用的安全性,它不仅能够屏蔽WEB应用固有弱... | sec-knowleage |
# Bypass 技巧
---
## 免责声明
`本文档仅供学习和研究使用,请勿使用文中的技术源码用于非法用途,任何人造成的任何负面影响,与本人无关.`
---
## 大纲
* [匹配绕过](#匹配绕过)
* [分段传输](#分段传输)
* [性能角度](#性能角度)
* [POST](#post)
---
**相关文章 & Source & Reference**
- [██大学通用型 WAF 不完全绕过(持续非定期更新) ](https://drivertom.blogspot.com/2018/12/waf.html)
- [技术讨论 | 在 HTTP 协议层面绕过 WAF](https://www.freebuf.com/n... | sec-knowleage |
package org.vulhub;
import org.springframework.context.annotation.Configuration;
import org.springframework.messaging.simp.config.MessageBrokerRegistry;
import org.springframework.web.socket.config.annotation.EnableWebSocketMessageBroker;
import org.springframework.web.socket.config.annotation.StompEndpointRegistry;
i... | sec-knowleage |
ssh-keyscan
===
收集主机公钥的使用工具
## 补充说明
**ssh-keyscan命令** 是一个收集大量主机公钥的使用工具。
### 语法
```shell
ssh-keyscan(选项)(参数)
```
### 选项
```shell
-4:强制使用IPv4地址;
-6:强制使用IPv6地址;
-f:从指定文件中读取“地址列表/名字列表”;
-p:指定连接远程主机的端口;
-T:指定连接尝试的超时时间;
-t:指定要创建的密钥类型;
-v:信息模式,打印调试信息。
```
### 参数
主机列表:指定要收集公钥的主机列表。 | sec-knowleage |
## ServerfARM (RE, 70p)
Description: Someone handed me this and told me that to pass the exam, I have to
extract a secret string. I know cheating is bad, but once does not count. So are
you willing to help me?
###ENG
[PL](#pl-version)
After reversing the provided ARM binary, we quickly find some print statements pri... | sec-knowleage |
实战中,需要用 bat 解决的事情总会碰到,而针对不同的环境,可能同一件事情需要不同的方案。
### demo:测试bat
bat 内容:追加到bat.txt里。


### 附代码:
```bash
Set oShell = CreateObject ("Wscript.Shell")
Dim strArgs
strArgs = "cmd /c bat.bat"
oShell.Run strArgs, 0, false
```
但是代码过长,... | sec-knowleage |
# 格基规约算法
## Lenstra–Lenstra–Lovasz
### 基本介绍
LLL 算法就是在格上找到一组基,满足如下效果
而且,这种方法生成的基所具有的如下性质是非常有用的
### 简单应用
这里我举一下 LLL paper 中给的第二个例子。给定 n 个实数 $\alpha_i,...,\alpha_n$,找到这 n 个数的有理线性逼近,即找到 n 个数 $m_i$,使得 $\sum\limits_{i=1}^{n}m_i\alpha_i$ 尽可能等于 0。 我们可以构造这样的矩阵,这里 $a_i$ 为 $\alpha_i$ 的有理逼近。
$$ A = \left[ \begin{matrix} 1 & 0 & ... | sec-knowleage |
version: '3'
services:
rmi:
build: "."
ports:
- 1099:1099
environment:
- RMIIP=192.168.31.88 | sec-knowleage |
# 杂项简介
Misc 是英文 Miscellaneous 的前四个字母,杂项、混合体、大杂烩的意思。
Misc 在国外的比赛中其实又被具体划分为各个小块,有
- Recon
- Forensic
- Stego
- Misc
- ……
在国内的比赛中,被统一划分入 Misc 领域,有时 Crypto(尤其是古典密码)也被划入其中。
在 Misc 这一章节中,将从以下几个方面介绍这一块的知识:
- Recon(信息搜集)
主要介绍一些获取信息的渠道和一些利用百度、谷歌等搜索引擎的技巧
- Encode(编码转换)
主要介绍在 CTF 比赛中一些常见的编码形式以及转换的技巧和常见方式
- ... | sec-knowleage |
**注:**请多喝点热水或者凉白开,可预防**肾结石,通风**等。
痛风可伴发肥胖症、高血压病、糖尿病、脂代谢紊乱等多种代谢性疾病。
**攻击机:**
192.168.1.5 Debian
**靶机:**
192.168.1.2 Windows 7
192.168.1.119 Windows 2003
### MSF的search支持type搜索:
```bash
msf > search scanner type:auxiliary
Matching Modules
================
Name Disclosure Date Rank Check Description
‐‐‐‐ ‐‐‐‐‐‐‐‐‐‐‐... | sec-knowleage |
# Writeup - noxCTF - believeMe ("Pwn" Category)
## Instructions:
What is going on here ?
I don't believe you...
you are crazy !!!
(No ASLR)
nc 18.223.228.52 13337
*[A binary file was attached as well]*
## Solution:
We connect to the supplied address and receive the following output:
```console
$ nc 18.223.228.52 13337... | sec-knowleage |
# T1059-001-win-检测Powershell下载文件
## 来自ATT&CK的描述
攻击者可能滥用PowerShell来执行命令和脚本。PowerShell是Windows操作系统中包含的功能强大的交互式命令行界面和脚本环境。攻击者可以使用PowerShell执行许多操作,包括发现信息和执行恶意代码。示例包括Start-Process可用于运行可执行文件的Invoke-Commandcmdlet和可在本地或远程计算机上运行命令的cmdlet(尽管使用PowerShell连接到远程系统需要管理员权限)。
PowerShell也可以用于从Internet下载并运行可执行文件,这些可执行文件可以从磁盘或内存中执行而无需接触磁盘... | sec-knowleage |
# 取证隐写前置技术
大部分的 CTF 比赛中,取证及隐写两者密不可分,两者所需要的知识也相辅相成,所以这里也将对两者一起介绍。
任何要求检查一个静态数据文件从而获取隐藏信息的都可以被认为是隐写取证题(除非单纯地是密码学的知识),一些低分的隐写取证又常常与古典密码学结合在一起,而高分的题目则通常用与一些较为复杂的现代密码学知识结合在一起,很好地体现了 Misc 题的特点。
## 前置技能
- 了解常见的编码
能够对文件中出现的一些编码进行解码,并且对一些特殊的编码(Base64、十六进制、二进制等)有一定的敏感度,对其进行转换并得到最终的 flag。
- 能够利用脚本语言(Python 等)去操作二进制数据
- ... | sec-knowleage |
# Postbook
## [Flag0](./flag0) -- Found
- The person with username "user" has a very easy password...
## [Flag1](./flag1) -- Found
- Try viewing your own post and then see if you can change the ID
## [Flag2](./flag2) -- Found
- You should definitely use "Inspect Element" on the form when creating a new post
## [Flag3](... | sec-knowleage |
# phpmyadmin 4.8.1 Remote File Inclusion Vulnerability (CVE-2018-12613)
[中文版本(Chinese version)](README.zh-cn.md)
PhpMyAdmin is a free software tool written in PHP, intended to handle the administration of MySQL over the Web. The vulnerability is in the `index.php`, causing files iclusion vulnerabilitiy.
Reference l... | sec-knowleage |
# AppSec-IL 2023
Writeups for several challenges from the [AppSec-IL 2023 CTF](https://appsecil2023.ctf.today/). | sec-knowleage |
# PHP 8.1.0-dev User-Agentt Backdoor
[中文版本(Chinese version)](README.zh-cn.md)
PHP version 8.1.0-dev was implanted with a backdoor on March 28, 2021, but the backdoor was quickly discovered and removed. When this backdoor is present on a server, an attacker can execute arbitrary code by sending a **User-Agentt** heade... | sec-knowleage |
.\" auto-generated by docbook2man-spec $Revision: 1.1 $
.TH "DROP GROUP" "7" "2003-11-02" "SQL - Language Statements" "SQL Commands"
.SH NAME
DROP GROUP \- 删除一个用户组
.SH SYNOPSIS
.sp
.nf
DROP GROUP \fIname\fR
.sp
.fi
.SH "DESCRIPTION 描述"
.PP
\fBDROP GROUP\fR 从数据库中删除指定的组。组中的用户不被删除。 组中的用户不被删除。
.SH "PARAMETERS 参数"
.TP
\fB\f... | sec-knowleage |
# 威胁狩猎实战
通过监控学校的官网,发现了一个访问次数非常大的一个IP:`115.239.194.82`,以此为目标来进行Hunting。
## 通过TI平台查询
### 通过微步查询该IP
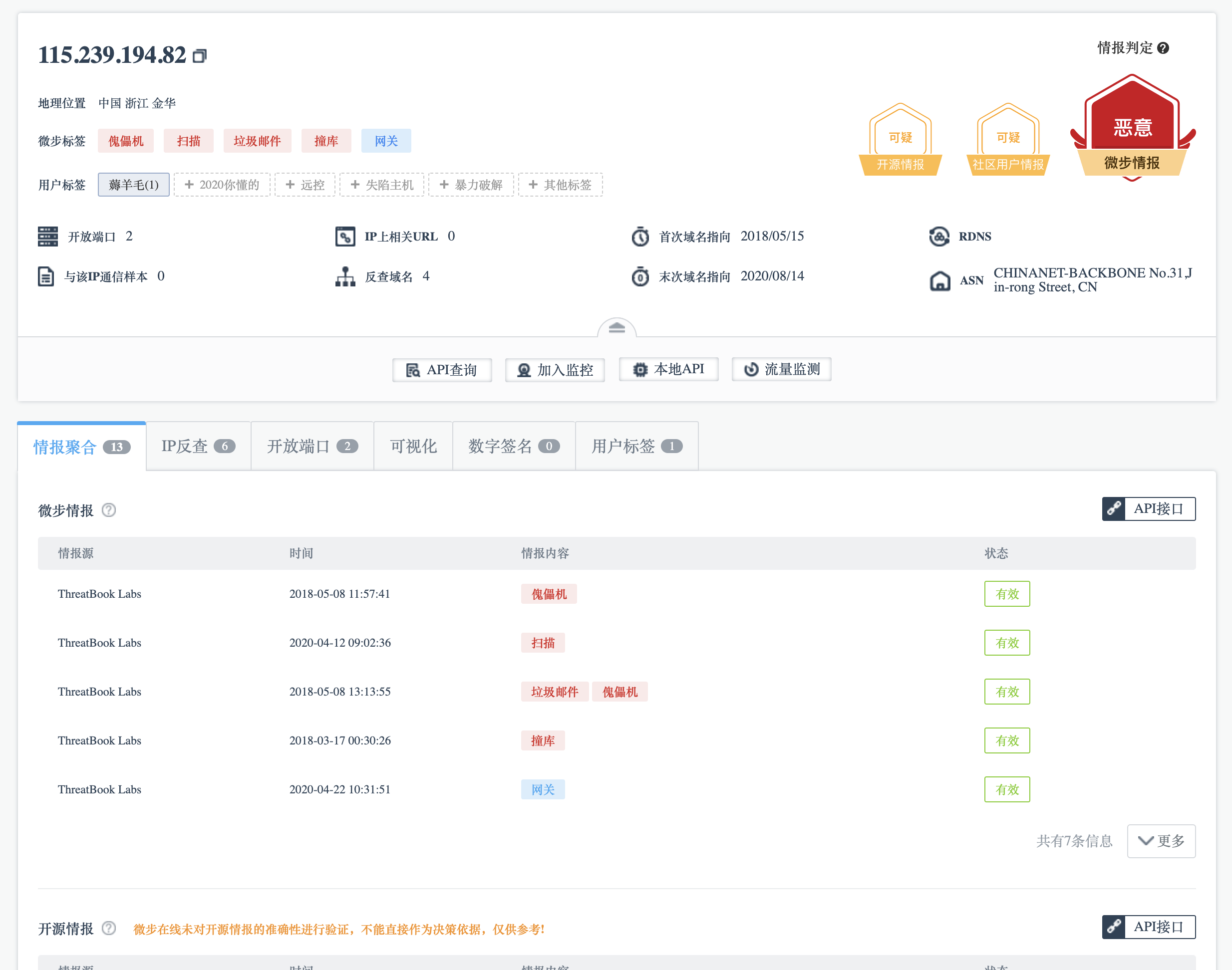
可以看到这个IP标签为:
- 僵尸网络
- 扫描
- 垃圾邮件
- 装库
- 撞库
- 网关
### 通过内部系统查看

This challenge is a pretty easy crypto challenge. What makes it surprising is
that it's very similar to WOTS which is a real world signature scheme.
We get a plaintext (something like `My favorite number is 123123123`) and a
valid signature. Our goal is to forge the signature.
The code ... | sec-knowleage |
---
title: 云服务
---
<center><h1>云服务</h1></center>
---
云服务,顾名思义就是云上的服务,简单的来说就是在云厂商(例如 AWS、阿里云)那里买的服务。
目前国内云厂商有阿里云、腾讯云、华为云、天翼云、Ucloud、金山云等等,国外有亚马逊的 AWS、Google 的 GCP、微软的 Azure 等等。
</br>
<img width="700" src="/img/1649992663.png">
</br></br>
各个云厂商对云服务的叫法都不统一,这里统一以 AWS 为例。
S3 对象存储`Simple Storage Service`,简单的说就是一个类似网盘的东西,当... | sec-knowleage |
# ASIS CTF 2018 Finals
Team: pwn.m0d3, shalom, nazywam, msm, rodbert, cr019283
### Table of contents
* [welcome (re)](re_welcome)
* [laxt (ppc)](ppc_laxt)
* [green cabbage (for)](for_cabbage)
* [made by baby (crypto)](crypto_baby)
* [Gunshop 1&2 (re/web)](re_gunshop)
* [John Bull (crypto)](crypto_john) | sec-knowleage |
# Weblogic Pre-Auth Remote Command Execution (CVE-2023-21839)
[中文版本(Chinese version)](README.zh-cn.md)
Oracle WebLogic Server is the industry leading application server for building enterprise applications using Java EE standards, and deploying them on a reliable, scalable runtime with low cost of ownership.
In [Ora... | sec-knowleage |
# JSON 学习笔记
---
**在线 JSON 格式化**
- https://www.json.cn/
- http://www.bejson.com/
- https://github.com/jsonhero-io/jsonhero-web
- https://jsonhero.io/
**JSONPath 在线查询工具**
- http://jsonpath.com/
**文章**
- [WORKING WITH DATA IN JSON FORMAT](https://www.trustedsec.com/blog/working-with-data-in-json-format/)
---
**什么是 JSO... | sec-knowleage |
# Time's Up, For the Last Time!
Reverse Engineering, 500 points
## Description:
> You've solved things fast. You've solved things faster! Now do the impossible.
## Solution:
This is the follow-up for [Time's Up, Again!](Times_Up_Again.md).
Let's run the attached file:
```console
root@kali:/media/sf_CTFs/pico/Times_Up_... | sec-knowleage |
# cereal hacker 2
Web Exploitation, 500 points
## Description:
> Get the admin's password.
## Solution:
This is the follow-up for [cereal hacker 1](cereal_hacker_1.md).
Again, we visit a similar website and receive the same login page:
```console
root@kali:/media/sf_CTFs/pico/cereal_hacker_2# curl https://2019shell1.p... | sec-knowleage |
# Graphene
* Category: Web
* 250 Points
* Solved by the JCTF Team
## Description
> Graphene is an easy to use CRM to manage leads.
>
> Some leads are VIP. Those are the most special ones.
## Solution
We visit the attached website and get a simple login page. If we check the sources, we see the following Javascript lo... | sec-knowleage |
## 一、什么是跨站脚本漏洞
跨站脚本漏洞(Cross Site Scripting,常简写作XSS)是Web应用程序在将数据输出到网页的时候存在问题,导致攻击者可以将构造的恶意数据显示在页面的漏洞。跟大多数Web 漏洞一样,此类漏洞的产生的原因也是没有处理好用户的输入。根据类型的不同,可以分为反射型 XSS,存储型 XSS,DOM 型 XSS,这篇先来讲讲反射型 XSS。
跨站脚本攻击注入的恶意代码运行在浏览器中,所以对用户的危害是巨大的——也需要看特定的场景:跨站脚本漏洞存在于一个无人访问的小站几乎毫无价值,但对于拥有大量用户的站点来说却是致命的。最典型的场景是,黑客可以利用跨站脚本漏洞盗取用户Cookie而得到用户在该站点... | sec-knowleage |
# sum
PWN
## Description:
> Sum it up!
An executable and libc-2.27.so were attached.
## Solution:
Let's see what the program does:
```
root@kali:/media/sf_CTFs/35c3ctf/sum# ./sum
---------------------
Simple Sum Calculator
---------------------
How many values to you want to sum up?
> 3
Allocated space for 3 values
Ent... | sec-knowleage |
# Spring Cloud Gateway Server 未授权访问漏洞
## 漏洞描述
Spring Cloud Gateway是Spring中的一个API网关。其3.1.0及3.0.6版本(包含)以前存在一处SpEL表达式注入漏洞,当攻击者可以访问Actuator API的情况下,将可以利用该漏洞执行任意命令。
## 环境搭建
执行如下命令启动一个使用了Spring Cloud Gateway 3.1.0的Web服务:
```
docker-compose up -d
```
服务启动后,访问`http://your-ip:8080`即可看到演示页面,这个页面的上游就是example.com。
![image-20220519... | sec-knowleage |
Subsets and Splits
Top 100 EPUB Books
This query retrieves a limited set of raw data entries that belong to the 'epub_books' category, offering only basic filtering without deeper insights.