text stringlengths 100 9.93M | category stringclasses 11
values |
|---|---|
# SaltStack 水平权限绕过漏洞(CVE-2020-11651)
SaltStack 是基于 Python 开发的一套C/S架构配置管理工具。国外某安全团队披露了 SaltStack 存在认证绕过漏洞(CVE-2020-11651)和目录遍历漏洞(CVE-2020-11652)。
在 CVE-2020-11651 认证绕过漏洞中,攻击者通过构造恶意请求,可以绕过 Salt Master 的验证逻辑,调用相关未授权函数功能,从而可以造成远程命令执行漏洞。
参考链接:
- https://labs.f-secure.com/advisories/saltstack-authorization-bypass
- https... | sec-knowleage |
# REQUIRED: PyCrypto 2.6.1
# To install: pip install pycrypto
# Homepage: https://www.dlitz.net/software/pycrypto/
import argparse
import SocketServer
import socket
import time
import sys
import json
import logging
from io import BytesIO
from base64 import b64encode, b64decode
from struct import pack, unpack
f... | sec-knowleage |
.\" auto-generated by docbook2man-spec $Revision: 1.1 $
.TH "CREATE LANGUAGE" "7" "2003-11-02" "SQL - Language Statements" "SQL Commands"
.SH NAME
CREATE LANGUAGE \- 定义一种新的过程语言
.SH SYNOPSIS
.sp
.nf
CREATE [ TRUSTED ] [ PROCEDURAL ] LANGUAGE \fIname\fR
HANDLER \fIcall_handler\fR [ VALIDATOR \fIvalfunction\fR ]
.sp
.... | sec-knowleage |
# Nginx 配置错误导致漏洞
## 运行测试环境
```
docker compose up -d
```
运行成功后,Nginx将会监听8080/8081/8082三个端口,分别对应三种漏洞。
## Mistake 1. CRLF注入漏洞
Nginx会将`$uri`进行解码,导致传入%0d%0a即可引入换行符,造成CRLF注入漏洞。
错误的配置文件示例(原本的目的是为了让http的请求跳转到https上):
```
location / {
return 302 https://$host$uri;
}
```
Payload: `http://your-ip:8080/%0d%0aSet-Cookie... | sec-knowleage |
# Apache Airflow Celery Broker Remote Command Execution (CVE-2020-11981)
[中文版本(Chinese version)](README.zh-cn.md)
Apache Airflow is an open source, distributed task scheduling framework. In the version prior to 1.10.10, if the Redis broker (such as Redis or RabbitMQ) has been controlled by attacker, the attacker can ... | sec-knowleage |
# Juicy Potato
ps:你要是翻译成好吃的土豆的的话,emmm,这人喜欢吃土豆,起的啥名?
我就翻译成可爱土豆了,咋滴。
[juicy-potato利用金票据提权](https://ohpe.github.io/juicy-potato/)
可爱土豆是`RottenPotato`漏洞利用的核武器级别的版本,利用微软处理令牌方式的原理,从而实现提权。
## 工作原理
我对Windows也并不是了解得有多深,但我就是想知道这个漏洞的原理。
`CLSID`是标识COM类对象的全局唯一标识符。这个漏洞允许我们从`session 0`中的服务帐户升级到SYSTEM权限。
## 怎么用呢?
我使用的是`Windows 10 Ente... | sec-knowleage |
# dctfizer (RevCrypt 400)
> Format Response: DCTF{md5(sol)} https://dctf.def.camp/quals-2016/re400.bin
> [UPDATE]: Initially it was MDCCCXLVI ...... don't even bother if you have nerve problems.
> [UPDATE] Updated ciphertext again. This time key was modified too! --- http://pastebin.com/r4BndGiy
In this task, we got ... | sec-knowleage |
.\" auto-generated by docbook2man-spec $Revision: 1.1 $
.TH "ALTER SEQUENCE" "7" "2003-11-02" "SQL - Language Statements" "SQL Commands"
.SH NAME
ALTER SEQUENCE \- 更改一个序列生成器的定义
.SH SYNOPSIS
.sp
.nf
ALTER SEQUENCE \fIname\fR [ INCREMENT [ BY ] \fIincrement\fR ]
[ MINVALUE \fIminvalue\fR | NO MINVALUE ] [ MAXVALUE \f... | sec-knowleage |
# 模板语法
Vue.js 使用了基于 HTML 的模板语法,允许开发者声明式地将 DOM 绑定至底层 Vue 实例的数据。所有 Vue.js 的模板都是合法的 HTML ,所以能被遵循规范的浏览器和 HTML 解析器解析。
在底层的实现上, Vue 将模板编译成虚拟 DOM 渲染函数。结合响应系统,在应用状态改变时, Vue 能够智能地计算出重新渲染组件的最小代价并应用到 DOM 操作上。
### 指令
带有 v- 前缀的特殊属性。指令属性的值预期是`单一 JavaScript 表达式`(除了 v-for,之后再讨论)。指令的职责就是当其表达式的值改变时相应地将某些行为应用到 DOM 上
**v-text**
```html
<s... | sec-knowleage |
.\"Copyright (c) 1995,1996,1999 by Internet Software Consortium
.\"
.\"Permission to use, copy, modify, and distribute this software for any
.\"purpose with or without fee is hereby granted, provided that the above
.\"copyright notice and this permission notice appear in all copies.
.\"
.\"THE SOFTWARE IS PROVIDED "AS ... | sec-knowleage |
# IPC$(Internet Process Connection)
---
## IPC$ 的概念
IPC`$`(Internet Process Connection) 是共享 "命名管道" 的资源,它是为了让进程间通信而开放的命名管道,可以通过验证用户名和密码获得相应的权限, 在远程管理计算机和查看计算机的共享资源时使用。
利用 IPC`$`,连接者可以与目标主机建立一个连接,利用这个连接,连接者可以得到目标主机上的目录结构、用户列表等信息。(当然, 对方机器必须开了 IPC$ 共享, 否则你是连接不上的)。
---
## IPC$ 与空连接、139、445、默认共享的关系
**IPC$ 与空连接**
不需要用户名与密码的 ... | sec-knowleage |
---
title: AWS 控制台接管
---
<center><h1>AWS 控制台接管</h1></center>
---
如果拿到了 AWS 凭证,可以进行控制台的接管,这里以 pacu 工具为例。
> 关于 AWS 凭证的获取可以看 [EC2 所面临的风险](/CloudService/EC2/) 部分的内容
pacu 工具里包含了很多 AWS 利用模块,首先使用 set_keys 命令将刚才获取到的 key 值添加到工具里。
</br><img width="600" src="/img/1649997441.png"></br>
接下来输入 console 命令,得到一个 URL。
</br>
<img width="... | sec-knowleage |
# Harmony Chat [283 points] (27 solves)
Files:
- This challenge provided a [link](http://harmony-1.hackable.software:3380/) and source ([harmony.zip](https://storage.googleapis.com/dragonctf-prod/harmony_301f77ba9efff83a832c0a31886c8d4a7aae39de1b9b3126fef5c7d4815b515f/harmony.zip))
## Part 0: research
At first sight, ... | sec-knowleage |
# 格式化输出
---
**Source & Reference**
- http://c.biancheng.net/view/41.html
---
格式化在逻辑中非常常用.使用格式化函数,要注意写法:
```
fmt.Sprintf(格式化样式, 参数列表…)
```
- 格式化样式:字符串形式,格式化动词以 % 开头.
- 参数列表:多个参数以逗号分隔,个数必须与格式化样式中的个数一一对应,否则运行时会报错.
```go
var progress = 2
var target = 8
// 两参数格式化
title := fmt.Sprintf("已采集%d个药草, 还需要%d个完成任务", progress, target... | sec-knowleage |
# Default Credentials
## Introduction
A Default Credential vulnerability is a type of vulnerability in a computing device that most commonly affects devices having some pre-set (default) administrative credentials to access all configuration settings.
## How to find
1. Find out type of CMS / Software is used by the web... | sec-knowleage |
version: '2.2'
services:
web:
image: vulhub/jetty:9.4.40
ports:
- "8080:8080"
volumes:
- ./src:/opt/jetty/webapps/ROOT | sec-knowleage |
---
title: 更新日志
---
<center><h1>更新日志</h1></center>
---
## 2023.8.18
<p></p>
<br>
<template>
<a-timeline><a-timeline-item>
<p>
<a-tag color="red">收到补充</a-tag>收到「苏打养乐多」师傅补充的文库信息,感谢支持,补充内容详情请见<a href="/cloudsecurityresources/" target="_blank"> 云安全资源 </a>版块,补充信息摘要如下:<br/>
<br/>
<ul>
... | sec-knowleage |
# fastjson
---
## 免责声明
`本文档仅供学习和研究使用,请勿使用文中的技术源码用于非法用途,任何人造成的任何负面影响,与本人无关.`
---
> 项目地址 : https://github.com/alibaba/fastjson
**相关文章**
- [Fastjson反序列化进攻利用](https://mp.weixin.qq.com/s/i7-g89BJHIYTwaJbLuGZcQ)
- [fastjson反序列化历史与检测](https://mp.weixin.qq.com/s/cCUYMiPsJnqHHdKHUno6UA)
- [Fastjson探测简介](https://mp.weixin.qq.com... | sec-knowleage |
# Writeup BITSCTF 2017
Team: c7f.m0d3, cr01283, msm, rev, shalom, akrasuski1, nazywam, psrok1
### Table of contents
* [ghost_in_the_machine (forensics)](ghost_in_the_machine)
* [enigma (crypto)](enigma)
* [sherlock (crypto)](sherlock)
* [beginners luck (crypto)](beginners_luck)
* [woodstock 1&2 (forensics)](woodstock)
... | sec-knowleage |
# 0x00 简介
这章主要讲下把shellcode加密然后解密运行,在前面几章讲过av一般都是杀的shellcode特征,msf的shellcode的加密后它就windows defender 就不认识它了。
其实每种语言都是一样的,这里用c# 因为它可以利用白名单执行,同时加密相对C/C++ 简单,但是可以看到它执行shell code代码量比C大多了。
# 0x01 加密shellcode
其实在GitHub上面很早就有大佬写了这些,还是那句话多搜索,多专研。
这里我直接用 `ShellcodeWrapper` (偷个懒精力有限达到效果就行)这款软件生成代码了,它的使用跟上章类似,只是转成CS,cpp,py文件需要自己编译一下... | sec-knowleage |
# cereal hacker 1
Web Exploitation, 450 points
## Description:
> Login as admin.
## Solution:
The website redirects to a login page:
```console
root@kali:/media/sf_CTFs/pico/cereal_hacker_1# curl https://2019shell1.picoctf.com/problem/49879/ -I
HTTP/1.1 302 Found
Server: nginx
Date: Tue, 15 Oct 2019 09:21:55 GMT
Conte... | sec-knowleage |
# InfluxDB Empty JWT Secret Key Authentication Bypass (CVE-2019-20933)
[中文版本(Chinese Version)](README.zh-cn.md)
InfluxDB is an open-source time series database developed by the company InfluxData.
InfluxDB before 1.7.6 has an authentication bypass vulnerability in the authenticate function in `services/httpd/handler... | sec-knowleage |
.\" @(#)lilo.conf.5 1.0 950728 aeb
.\" This page is based on the lilo docs, which carry the following
.\" COPYING condition:
.\"
.\" LILO program code, documentation and auxiliary programs are
.\" Copyright 1992-1994 Werner Almesberger.
.\" All rights reserved.
.\"
.\" Redistribution and use in source and binary forms... | sec-knowleage |
# ossa(open-source security architecture)
[开源安全架构](https://bloodzer0.github.io/ossa/)
如果愿意分享或者想给我一些更多的意见,欢迎加我微信:**Lzero2012**
## 致过去
本项目从2018-10-08号开始创建,截止目前2个月多一点,star目前在400+,很感谢大家的支持,写东西一直是一件很累的事情,但是我一直在努力下去。
过去的2个月写了很多开源安全工具的安装与使用,也有很多人提出了质疑"不应该把项目写成了工具文章",套用前几天看到的一句话:"安装与使用我不会去看官方文档嘛"。这里给自己解释一下,一开始我的方向就是利用开源工具来建设中小... | sec-knowleage |
# picoCTF - 2021
Writeups for various challenges from the 2021 [picoCTF competition](https://play.picoctf.org/).
Ranking at the buzzer: 86/6215 with 5640 points. | sec-knowleage |
ethtool
===
显示或修改以太网卡的配置信息
## 补充说明
ethtool命令用于获取以太网卡的配置信息,或者修改这些配置。这个命令比较复杂,功能特别多。
### 语法
```shell
ethtool [ -a | -c | -g | -i | -d | -k | -r | -S |] ethX
ethtool [-A] ethX [autoneg on|off] [rx on|off] [tx on|off]
ethtool [-C] ethX [adaptive-rx on|off] [adaptive-tx on|off] [rx-usecs N] [rx-frames N] [rx-usecs-irq N] [... | sec-knowleage |
# PHP-FPM Fastcgi 未授权访问漏洞
## 原理
详见<https://www.leavesongs.com/PENETRATION/fastcgi-and-php-fpm.html>。
## 测试环境搭建
直接执行`docker compose up -d`即可运行测试环境,环境监听9000端口。
## EXP
Exp见 https://gist.github.com/phith0n/9615e2420f31048f7e30f3937356cf75
执行结果:
 | sec-knowleage |
# Postbook - FLAG6
## 0x00 Delet Post
http://127.0.0.1/1234567890/index.php?page=delete.php&id=eccbc87e4b5ce2fe28308fd9f2a7baf3
Where **id=eccbc87e4b5ce2fe28308fd9f2a7baf3** is also [md5][1] value of post id.

## 0x01 Delete Others
http://127.0.0.1/1234567890/index.php?page=delete.php&id=c4ca4238a... | sec-knowleage |
dpkg-deb
===
Debian Linux下的软件包管理工具
## 补充说明
**dpkg-deb命令** 是Debian Linux下的软件包管理工具,它可以对软件包执行打包和解包操作以及提供软件包信息。
### 语法
```shell
dpkg-deb(选项)(参数)
```
### 选项
```shell
-c:显示软件包中的文件列表;
-e:将主控信息解压;
-f:把字段内容打印到标准输出;
-x:将软件包中的文件释放到指定目录下;
-X:将软件包中的文件释放到指定目录下,并显示释放文件的详细过程;
-w:显示软件包的信息;
-l:显示软件包的详细信息;
-R:提取控制信息和存档的清单文件;
-b:创建debia... | sec-knowleage |
partprobe
===
不重启的情况下重读分区
## 补充说明
**partprobe命令** 用于重读分区表,当出现删除文件后,出现仍然占用空间。可以partprobe在不重启的情况下重读分区。
### 语法
```shell
partprobe(选项)(参数)
```
### 选项
```shell
-d:不更新内核;
-s:显示摘要和分区;
-h:显示帮助信息;
-v:显示版本信息。
```
### 参数
设备:指定需要确认分区表改变的硬盘对应的设备文件。
### 实例
使用partprobe不重启系统添加新的磁盘分区,主机自带硬盘超过300GB,目前只划分使用了3个主分区,不到70GB,如下:
```shell
... | sec-knowleage |
### misc测试支持
下面的代码用于支持测试,默认情况下 perturb_byte 是0。
```c
static int perturb_byte;
static void alloc_perturb(char *p, size_t n) {
if (__glibc_unlikely(perturb_byte)) memset(p, perturb_byte ^ 0xff, n);
}
static void free_perturb(char *p, size_t n) {
if (__glibc_unlikely(perturb_byte)) memset(p, perturb_byte, n);
}
``... | sec-knowleage |
# MacroHard WeakEdge
Category: Forensics, 60 points
## Description
> I've hidden a flag in this file. Can you find it?
A `*.pptm` file was attached.
## Solution
The attached file is a PowerPoint presentation:
```console
┌──(user@kali)-[/media/sf_CTFs/pico/MacroHard_WeakEdge]
└─$ file Forensics_is_fun.pptm
Forensics_is_... | sec-knowleage |
'\"
'\" Copyright (c) 1993-1997 Bell Labs Innovations for Lucent Technologies
'\" Copyright (c) 1997 Sun Microsystems, Inc.
'\"
'\" See the file "license.terms" for information on usage and redistribution
'\" of this file, and for a DISCLAIMER OF ALL WARRANTIES.
'\"
'\" RCS: @(#) $Id: variable.n,v 1.2 2003/11/24 05:10... | sec-knowleage |
# #RSA
Category: Cryptography
## Description
> We found a weird service running on a server in the department of EEvil, please figure out what you can do with it and report back.
## Solution
Let's connect to the attached service:
```console
root@kali:/media/sf_CTFs/technion/RSA# nc ctf.cs.technion.ac.il 4002
n: 2490424... | sec-knowleage |
.\" DO NOT MODIFY THIS FILE! It was generated by help2man 1.48.5.
.\"*******************************************************************
.\"
.\" This file was generated with po4a. Translate the source file.
.\"
.\"*******************************************************************
.TH UNAME 1 2022年9月 "GNU coreutils 9.... | sec-knowleage |
# T1588-003-获取能力-代码签名证书
## 来自ATT&CK的描述
攻击者可能会购买或窃取代码签名证书,以便在攻击目标中使用。代码签名是对可执行文件和脚本进行数字签名的过程,以确认软件的作者并保证代码没有被改变或破坏。代码签名为程序的开发者提供了一定程度的真实性,并保证程序没有被篡改。用户和安全工具可能比未签名的代码更信任已签名的代码,即使他们不知道谁颁发了证书或谁是作者。
在代码签名之前,攻击者可能会购买或窃取代码签名证书用于操作。购买代码签名证书可以使用一个幌子组织,或使用从以前被攻破的实体中窃取的信息,使攻击者能够以该实体的身份向证书提供商验证。攻击者也可以直接从被攻击的第三方那里窃取代码签名材料。
## 测试案例
... | sec-knowleage |
# H2 Database Console 未授权访问
H2 database是一款Java内存数据库,多用于单元测试。H2 database自带一个Web管理页面,在Spirng开发中,如果我们设置如下选项,即可允许外部用户访问Web管理页面,且没有鉴权:
```
spring.h2.console.enabled=true
spring.h2.console.settings.web-allow-others=true
```
利用这个管理页面,我们可以进行JNDI注入攻击,进而在目标环境下执行任意命令。
参考链接:
- <https://mp.weixin.qq.com/s?__biz=MzI2NTM1MjQ3OA=... | sec-knowleage |
### Hello React
#### 初始化一个项目react-hello
```
create-react-app react-hello
```
**注意**:不要出现项目套项目,仓库套仓库。项目名称不要取包名(react...)。
#### 启动项目
```
npm start
```
成功启动说明项目成功初始化
#### 退出项目
```
ctrl + C
```
#### 修改项目
删除src文件夹重新创建一个src
```
rm -rf src && mkdir src
```
在src下新建一个index.js并返回项目文件夹
```
cd src && touch index.js && cd ..
```
**... | sec-knowleage |
#!/usr/bin/env python
"""Django's command-line utility for administrative tasks."""
import os
import sys
def main():
os.environ.setdefault('DJANGO_SETTINGS_MODULE', 'CVE20209402.settings')
try:
from django.core.management import execute_from_command_line
except ImportError as exc:
raise Im... | sec-knowleage |
exec
===
调用并执行指定的命令
## 补充说明
**exec命令** 用于调用并执行指令的命令。exec命令通常用在shell脚本程序中,可以调用其他的命令。如果在当前终端中使用命令,则当指定的命令执行完毕后会立即退出终端。
### 语法
```shell
exec(选项)(参数)
```
### 选项
```shell
-c:在空环境中执行指定的命令。
```
### 参数
指令:要执行的指令和相应的参数。
### 实例
首先使用echo命令将文本“Linux C++”进行输出,输入如下命令:
```shell
echo Linux C++ # 输出指定信息
```
执行上面的指令后,输出如下信... | sec-knowleage |
# noxtis CTF - 2019
## Background
> noxtis is a collection of challenges dedicated for second year students at Magshimim. Its goal is to further expose the students to the world of cyber security through a variety of security challenges in different areas of the realm.
## Storyline
> Last Saturday Nahman, the creator ... | sec-knowleage |
# Burp Suite
## Burp Suite 包描述
Burp Suite是一个用于执行Web应用程序安全测试的集成平台。 它的各种工具无缝地协同工作,支持整个测试过程,从初始映射和分析应用程序的攻击面,到查找和利用安全漏洞。
Burp让您完全控制,让您结合先进的手动技术与先进的自动化,使您的工作更快,更有效,更有趣。
资料来源:http://portswigger.net/burp/
[Burp Suite 主页](http://portswigger.net/) | [Burp Suite 主页](http://git.kali.org/gitweb/?p=packages/burpsuite.git;a=summary... | sec-knowleage |
# Django debug page XSS漏洞(CVE-2017-12794)分析
Django发布了新版本1.11.5,修复了500页面中可能存在的一个XSS漏洞,这篇文章说明一下该漏洞的原理和复现,和我的一点点评。
## 0x01 补丁分析
因为官方说明是500页面中出现的BUG,所以我们重点关注的就是`django/views/debug.py`。
Github上有Django的仓库,下载下来,用1.11.4和1.11.5进行比较:
```bash
git clone https://github.com/django/django.git
cd django
git diff 1.11.4 1.11.5 dja... | sec-knowleage |
# Enigma (crypto)
```
Its World War II and Germans have been using Enigma to encrypt their messages. Our analysts have figured that they might be using XOR-encryption. XOR-encrption is vulnerable to a known-plaintext attack. Sadly all we have got are the encrypted intercepted messages. Your task is to break the Enigma ... | sec-knowleage |
# Bugler
* Category: Web
* 550 Points
* Solved by the JCTF Team
## Description
> Don't be so selfish! Share your phishing sites with us, our admin will appreciate your service
>
> URL: https://bugler.ctf.bsidestlv.com
>
> By Daniel Abeles and Tomer Zait
## Solution
The attached website is an impressive dashboard with... | sec-knowleage |
'\"
'\" Copyright (c) 1996 Sun Microsystems, Inc.
'\"
'\" See the file "license.terms" for information on usage and redistribution
'\" of this file, and for a DISCLAIMER OF ALL WARRANTIES.
'\"
'\" RCS: @(#) $Id: fblocked.n,v 1.2 2003/11/24 05:09:59 bbbush Exp $
'\" The definitions below are for supplemental macros use... | sec-knowleage |
# dkdos
Reversing, 45 points
## Description
> I've sent my KIPODIM shop to a friend of mine, and he told me he was able to access it with just a random password. Can you please check it?
A binary file was attached.
## Solution
Let's check the file:
```console
root@kali:/media/sf_CTFs/kaf/dkdos# file dkdos.exe
dkdos.exe... | sec-knowleage |
# Primordial (Crypto, 171p, 25 solved)
In the challenge we get [code](primordial_rsa.py) and [output](output.txt).
If we look at the primes generation, some things seems odd:
```python
def gen_prime(nbit):
while True:
s = getPrime(36)
a = primorial(getPrime(random.randint(7, 9)))
b = primori... | sec-knowleage |
import re
from Crypto.Util.number import bytes_to_long
from crypto_commons.generic import chunk
from riscv_asm import TYPES_TO_INSTRUCTION, INSTRUCTION_TO_TYPE, OPCODES, FUNCT_CODES, \
R_I_TYPE_UPPER_SEVEN_BITS_NORMAL, R_I_TYPE_UPPER_SEVEN_BITS_ALT, LOAD_INSTRUCTION_NAMES, STORE_INSTRUCTION_NAMES
import argparse
... | sec-knowleage |
.\" Copyright (c) 1993 Free Software Foundation
.\" See section COPYING for conditions for redistribution
.TH strings 1 "25 June 1993" "cygnus support" "GNU Development Tools"
.de BP
.sp
.ti \-.2i
\(**
..
.SH NAME
strings \- 显示文件中的可打印字符
.SH "总览 (SYNOPSIS)"
.hy 0
.na
.TP
.B strings
.RB "[\|" \-a | \-\c
.RB | \-\-all "\|... | sec-knowleage |
# picoCTF - 2018
Writeups for various challenges from the 2018 [picoCTF competition](https://2018game.picoctf.com/).
 | sec-knowleage |
# T1003-windows-Procdump明文凭证
## 来自ATT&CK的描述
凭证获取是从操作系统和软件中获取登录信息和密码的过程,通常为HASH散列或明文密码。然后使用凭证进行横向移动访问其他系统。
用户登录系统后,会生成各种凭据并将其存储在内存中的本地安全机构子系统服务(LSASS)进程中。这些凭证可以由管理用户或SYSTEM进行管理。
SSPI是Security Support Provider Interface(Microsoft安全支持提供器接口)的英文缩写。安全支持提供程序接口(SSPI)允许应用程序使用计算机或网络上可用的各种安全模型,而无需更改安全系统的接口。SSPI不会记录登录凭据,因为这通常是操作系统... | sec-knowleage |
version: '2'
services:
web:
image: vulhub/imagemagick:6.9.2-10-php
command: php -t /var/www/html -S 0.0.0.0:8080
volumes:
- ./index.php:/var/www/html/index.php
ports:
- "8080:8080" | sec-knowleage |
# 工具介绍 Veil-Evasion
项目地址:
https://github.com/Veil-Framework/Veil-Evasion
### 1、Veil-Evasion
Veil-Evasion 是与 Metasploit 生成相兼容的 Payload 的一款辅助框架,并可以绕过大多数的杀软。
Veil-Evasion 并没有集成在kali,配置 sources.list,可直接 apt-get。
```bash
root@John:~/Deskto#cat /etc/apt/sources.list
#中科大
deb http://mirrors.ustc.edu.cn/kali kali-rolling mai... | sec-knowleage |
## OPM (Misc, 3p)
###ENG
[PL](#pl-version)
In this task, we got only an image - so the first step was probably solving a stegano task.
Using Stegsolve, we quickly see that least significant bits of all three channels (R,G,B) contain
semi-random data on top of the image, and are totally black on the bottom. Extracting d... | sec-knowleage |
volname
===
显示指定的ISO-9660格式的设备的卷名称
## 补充说明
**volname命令** 用于显示指定的“ISO-9660”格式的设备的卷名称,通常这种格式的设备为光驱。
### 语法
```shell
volname(参数)
```
### 参数
设备文件名:指定要显示卷名称的设备。 | sec-knowleage |
arping
===
通过发送ARP协议报文测试网络
## 补充说明
**arping命令** 是用于发送arp请求到一个相邻主机的工具,arping使用arp数据包,通过ping命令检查设备上的硬件地址。能够测试一个ip地址是否是在网络上已经被使用,并能够获取更多设备信息。功能类似于ping。
### 语法
```shell
arping(选项)(参数)
```
### 选项
```shell
-b:用于发送以太网广播帧(FFFFFFFFFFFF)。arping一开始使用广播地址,在收到响应后就使用unicast地址。
-q:quiet output不显示任何信息;
-f:表示在收到第一个响应报文后就退出;
-w timeou... | sec-knowleage |
### KASLR的开启与关闭
如果是使用 qemu 启动的内核,我们可以在 `-append` 选项中添加 `kaslr` 来开启 KASLR。
如果是使用 qemu 启动的内核,我们可以在 `-append` 选项中添加 `nokaslr` 来关闭 KASLR。 | sec-knowleage |
mkdir
===
用来创建目录
## 补充说明
**mkdir命令** 用来创建目录。该命令创建由dirname命名的目录。如果在目录名的前面没有加任何路径名,则在当前目录下创建由dirname指定的目录;如果给出了一个已经存在的路径,将会在该目录下创建一个指定的目录。在创建目录时,应保证新建的目录与它所在目录下的文件没有重名。
注意:在创建文件时,不要把所有的文件都存放在主目录中,可以创建子目录,通过它们来更有效地组织文件。最好采用前后一致的命名方式来区分文件和目录。例如,目录名可以以大写字母开头,这样,在目录列表中目录名就出现在前面。
在一个子目录中应包含类型相似或用途相近的文件。例如,应建立一个子目录,它包含所有的数据库文... | sec-knowleage |
import random
from crypto_commons.generic import bytes_to_long, multiply, factor, long_to_bytes
from crypto_commons.netcat.netcat_commons import nc, receive_until_match, receive_until, send
from crypto_commons.rsa.rsa_commons import gcd_multi
def prepare_values():
prefix = bytes_to_long("X: ")
factors, _ = f... | sec-knowleage |
# EOP, re
This task was a reverse engineering challenge with binary using exceptions as control flow (post
factum we noticed name of the task may mean Exception Oriented Programming). Each exception
handler did just a tiny bit of computation on global state and set up another exception to be thrown.
Thankfully, there w... | sec-knowleage |
wall
===
向系统当前所有打开的终端上输出信息
## 补充说明
**wall命令** 用于向系统当前所有打开的终端上输出信息。通过wall命令可将信息发送给每位同意接收公众信息的终端机用户,若不给予其信息内容,则wall命令会从标准输入设备读取数据,然后再把所得到的数据传送给所有终端机用户。
### 语法
```shell
wall(参数)
```
### 参数
消息:指定广播消息。
### 实例
```shell
[root@localhost ~]# wall this is a test line
Broadcast message from root (pts/1) (Fri Dec 20 11:36:51 20... | sec-knowleage |
---
title: MIME types
date: 2020-04-03 17:28:43
tags:
- media type
categories:
- Other
intro: |
This cheat sheet lists some common MIME types for the Web. You can look in the [IANA/MIME Media Types registry](http://www.iana.org/assignments/media-types/index.html) which contains all registered MIME types.
--... | sec-knowleage |
### CSRF 简介
CSRF,全名 Cross Site Request Forgery,跨站请求伪造。很容易将它与 XSS 混淆,对于 CSRF,其两个关键点是跨站点的请求与请求的伪造,由于目标站无 token 或 referer 防御,导致用户的敏感操作的每一个参数都可以被攻击者获知,攻击者即可以伪造一个完全一样的请求以用户的身份达到恶意目的。
### CSRF 类型介绍
按请求类型,可分为 GET 型和 POST 型。
按攻击方式,可分为 HTML CSRF、JSON HiJacking、Flash CSRF 等。
### HTML CSRF请求方式
利用 HTML 元素发出 CSRF 请求,这是最常见的 CSRF 攻击。... | sec-knowleage |
## 开发工具
| Exploitation Tools | | | | | |
| :----------------------------------------------------------: | :---------------------------------... | sec-knowleage |
# MSSQL
---
## MSSQL 系统库
- master : master 数据库控制 SQLserver 数据库所有方面。这个数据库中包括了所有的配置信息、用户登录信息、当前正在服务器中运行的过程的信息等。
- model : model 数据库是建立所有用户数据库时的模版。新建数据库时,SQLserver 会把 model 数据库中的所有对象建立一份拷贝并移到新数据库中。在模版对象被拷贝到新的用户数据库中之后,该数据库的所有多余空间都将被空页填满。
- tempdb : tempdb 数据库是一个非常特殊的数据库,供所有访问 SQLserver 数据库的用户使用。这个库用来保存所有的临时表、存储过程和其他 SQLser... | sec-knowleage |
---
title: Principle
date: 2022-11-23 16:23:31.698567
background: bg-[#b245c6]
label: Mac
tags:
-
- mac
categories:
- Keyboard Shortcuts
intro: |
A visual cheat-sheet for the 30 keyboard shortcuts found in Principle. This application is MacOS-only.
---
Keyboard Shortcuts
------------------
### Layers ... | sec-knowleage |
# Brainary
Category: Cryptography
## Description
> It stares at the endless abyss of darkness. The abyss reflects. Knowing it can never see light again, it seeks the truth.
>
> The universe reveals its mysteries through endless streams of numericals.
>
> Burned with the passion to learn, the raven child seeks new way... | sec-knowleage |
.\" auto-generated by docbook2man-spec $Revision: 1.1 $
.TH "CREATE GROUP" "7" "2003-11-02" "SQL - Language Statements" "SQL Commands"
.SH NAME
CREATE GROUP \- 定义一个新的用户组
.SH SYNOPSIS
.sp
.nf
CREATE GROUP \fIname\fR [ [ WITH ] \fIoption\fR [ ... ] ]
where \fIoption\fR can be:
SYSID \fIgid\fR
| USER \fIusername\... | sec-knowleage |
spell
===
对文件进行拼写检查
## 补充说明
**spell命令** 对文件进行拼写检查,并把拼写错误的单词输出。
### 语法
```shell
spell(参数)
```
### 参数
文件:指定需要进行拼写检查的文件。 | sec-knowleage |
# m00nwalk
Forensics, 250 points
## Description:
> Decode this message from the moon.
A WAV file was attached.
Hints:
* How did pictures from the moon landing get sent back to Earth?
* What is the CMU mascot?, that might help select a RX option
## Solution:
Nothing meaningful can be identified listening to the file. A... | sec-knowleage |
##smartcat (Web, 50+50p)
###PL
[ENG](#eng-version)
W zadaniu dostajemy do dyspozycji webowy interfejs (CGI) pozwalający pignować wskazanego hosta.
Domyślamy się, że pod spodem operacja jest realizowana jako wywołanie `ping` w shellu z doklejonym podanym przez nas adresem.
#### Smartcat1
Pierwsza część zadania polega ... | sec-knowleage |
expected = 'efda2f556de36b9e9e1d62417c5f282d8961e2f8' # level 1
expected = '354ebf392533dce06174f9c8c093036c138935f3' # level 2
expected = 'd961f81a588fcfd5e57bbea7e17ddae8a5e61333' # level 3
expected = 'f8d0839dd728cb9a723e32058dcc386070d5e3b5' # level 4
d = open('sharp_v4_f8d0_8096').read()
def githash(d):
impo... | sec-knowleage |
原文 by MayIKissYou
## 0x01 HTML中嵌入FLASH
在HTML中嵌入FLASH的时候在IE和非IE浏览器下嵌入的方式有所不同,可以使用embed 标签和object 标签,使用如下的代码进行嵌入:
IE下嵌入
``` html
<object codeBase="http://fpdownload.macromedia.com/get/Flashplayer/current/swFlash.cab#version=8,0,0,0"
classid="clsid:D27CDB6E-AE6D-11cf-96B8-444553540000">
<param name="movie" value = ... | sec-knowleage |
# Spring Data Commons 远程命令执行漏洞(CVE-2018-1273)
Spring Data是一个用于简化数据库访问,并支持云服务的开源框架,Spring Data Commons是Spring Data下所有子项目共享的基础框架。Spring Data Commons 在2.0.5及以前版本中,存在一处SpEL表达式注入漏洞,攻击者可以注入恶意SpEL表达式以执行任意命令。
参考链接:
- https://pivotal.io/security/cve-2018-1273
- https://xz.aliyun.com/t/2269
- https://mp.weixin.qq.com/s?__biz=... | sec-knowleage |
### mips - ROP预备知识
架构回顾见: https://ctf-wiki.github.io/ctf-wiki/assembly/mips/readme-zh/
栈结构如图:
有几个特殊的地方需要注意
1. MIPS32架构中是没有EBP寄存器的,程序函数调用的时候是将当前栈指针向下移动 n 比特到该函数的 stack frame 存储组空间,函数返回的时候再加上偏移量恢复栈
2. 传参过程中,前四个参数$a0-$a3,多余的会保存在调用函数的预留的栈顶空间内
3. MIPS调用函数... | sec-knowleage |
---
title: 移动恶意代码分析及威胁情报
date: 2020-01-15 23:45:58
tags: 移动安全
---
# 移动恶意应用分析

图:背景
## 恶意代码分析背景概述
### 背景
1.全面的移动威胁
2.移动生态环节面临的安全威胁
表面:黑灰产
里面:国家队
3.攻击手段的持续进化
4.恶意色情软件增长趋势
一般不用支付宝、微信,使用第三方
5.地下社工库
- 完成原始数据积累
- 完善的黑产分工协作体系
6.持续扩大的威胁面
<img src="http... | sec-knowleage |
### VDSO介绍
什么是VDSO(Virtual Dynamically-linked Shared Object)呢?听其名字,大概是虚拟动态链接共享对象,所以说它应该是虚拟的,与虚拟内存一致,在计算机中本身并不存在。具体来说,它是将内核态的调用映射到用户地址空间的库。那么它为什么会存在呢?这是因为有些系统调用经常被用户使用,这就会出现大量的用户态与内核态切换的开销。通过vdso,我们可以大量减少这样的开销,同时也可以使得我们的路径更好。这里路径更好指的是,我们不需要使用传统的int 0x80来进行系统调用,不同的处理器实现了不同的快速系统调用指令
- intel实现了sysenter,sysexit
- amd实现了sysc... | sec-knowleage |
grpunconv
===
用来关闭群组的投影密码
## 补充说明
**grpunconv命令** 用来关闭群组的投影密码。它会把密码从gshadow文件内,回存到group文件里。
### 语法
```shell
grpunconv
```
### 实例
未关闭的情况
```shell
cat /etc/gshadow | grep cdy
cdy:123456::
```
关闭影子密码
```shell
cat /etc/gshadow
cat: /etc/gshadow: 没有那个文件或目录
```
查看密码已经复制到`/etc/group`中了。
```shell
cat /etc/group | grep cdy
cd... | sec-knowleage |
# PySandbox 1 (misc, 121p, 52 solved)
```
nc pwn1.chal.ctf.westerns.tokyo 30001
```
In the challenge we get access to server which executes provided python code, as long as it passed the [sandbox](sandbox.py).
The sandbox parses the code into AST and then blacklists function calls and attribute access.
So we can for ex... | sec-knowleage |
# 机器学习算法实现
本小章节主要记录我学习机器学习算法,并代码实现的过程。
参考项目:
- 机器学习算法Python实现,https://github.com/lawlite19/MachineLearning_Python
- AI learning,https://github.com/apachecn/AiLearning
- Machine-Learning-With-Python,https://github.com/Thinkgamer/Machine-Learning-With-Python
- 斯坦福机器学习笔记,https://github.com/yoyoyohamapi/mit-ml | sec-knowleage |
# Episode 0: Challenge 2
## Description
> After recent attacks, we’ve developed a search tool. Search the logs and discover what the attackers were after.
>
> Hint: Always search deeper.
A link to an online log search tool was attached.
## Solution
The link leads us to an online log search tool. The search term defau... | sec-knowleage |
# Writeup Boston Key Party 2017
Team: c7f.m0d3, cr01283, akrasuski1, nazywam, shalom, msm, rev
### Table of contents
* [RSA buffet(crypto)](rsa_buffet)
* [VimJail (pwn)](vimjail)
* [Artisinal Shoutboxes (web)](cloud_200_artisinal_shoutboxes)
* [Minesweeper (crypto)](minesweeper)
* [Signed Shell Server (pwn)](signed_she... | sec-knowleage |
### Chunk Extend and Overlapping介绍
chunk extend是堆漏洞的一种常见利用手法,通过extend可以实现chunk overlapping的效果。这种利用方法需要以下的时机和条件:
* 程序中存在基于堆的漏洞
* 漏洞可以控制 chunk header 中的数据
### Chunk Extend and Overlapping原理
chunk extend技术能够产生的原因在于ptmalloc在对堆chunk进行操作时使用的各种宏。
在ptmalloc中,获取 chunk 块大小的操作如下
```
/* Get size, ignoring use bits */
#define chunk... | sec-knowleage |
# 简介
[
[
[
欢迎来到 **CTF Wiki**。
**CTF**(Capture The Flag,夺旗赛)起源于 1996 年 **DEFCON** 全球黑客大会,是网络安全爱好者之间的竞技游戏。
**CTF** 竞赛涉及众多领域,内容繁杂。与此同时,安全技术的发展速度越来越快,**CTF** 题目的难度越来越高,初学者面对的门槛越来越高。而网上资料大都零散琐碎,初学者往往并不知道该如何系统性地学习 **CTF** 相关领域知识,常需要花费大量时间,苦不堪言。
为了使得热爱 **CTF** 的小伙伴们更好地入门 **CTF**,2016 年 10 月份,**CTF Wiki** 在 Github 有了第一次 commit... | sec-knowleage |
# pupy
---
## 免责声明
`本文档仅供学习和研究使用,请勿使用文中的技术源码用于非法用途,任何人造成的任何负面影响,与本人无关.`
---
**项目地址**
- https://github.com/n1nj4sec/pupy
**相关文章**
- [pupy安装与使用](https://mp.weixin.qq.com/s/7VyJHHvUHITY61RC8VveOQ)
- [Pupy利用分析——Windows平台下的功能](https://3gstudent.github.io/Pupy%E5%88%A9%E7%94%A8%E5%88%86%E6%9E%90-Windows%E5%B9%B3%E5%8F%B0%E4%... | sec-knowleage |
# Wrestler Name Generator
Web, 150 points
## Description
> Even better than the Wu-Tang name generator, legend has it that Hulk Hogan used this app to get his name.
## Solution
We visit the attaches site and see a form:
```html
<form>
<div class="form-group">
<label style="color:white" for="exampleFormControlInpu... | sec-knowleage |
## Orgone Market (Web, 300p)
###ENG
[PL](#pl-version)
In the task we get a link to a webpage where we can buy some conspiracy-related objects for special orgone coins.
However we have 0 coins and those things cost!
There is a form on the page to claim free 300 coins, but this is not enough to buy anything on the page.
... | sec-knowleage |
package org.vulhub.shirodemo;
import org.apache.shiro.mgt.RememberMeManager;
import org.apache.shiro.mgt.SecurityManager;
import org.apache.shiro.spring.web.ShiroFilterFactoryBean;
import org.apache.shiro.web.mgt.CookieRememberMeManager;
import org.apache.shiro.web.mgt.DefaultWebSecurityManager;
import org.springframe... | sec-knowleage |
from flask import Flask, abort, redirect, request, Response
from flask_graphql import GraphQLView
from model import db_session, Attachment
from schema import schema
app = Flask(__name__)
@app.route('/')
def main():
return 'GraphiQL'
@app.route('/attachment/')
@app.route('/attachments/')
def attachment(id):... | sec-knowleage |
##CatchMeIfYouCan (Forensics, 100p)
We got this log which is highly compressed. Find the intruder's secret.
###PL
[ENG](#eng-version)
Plik f100 jest pewnego rodzaju Matryoshką kompresyjną, plik trzeba kolejno rozkompresowywać różnymi mniej i bardziej znanymi formatami. Po chwili okazuje się, że plik jest dosyć "głębo... | sec-knowleage |
# Super Serial
Category: Web, 130 points
## Description
> Try to recover the flag stored on this website
>
> Hint: The flag is at ../flag
## Solution
The attached website just contains a username and password:
```html
<form class="form-signin" action="index.php" method="post">
<div class="form-label-group">
<input... | sec-knowleage |
tee
===
从标准输入读取数据并重定向到标准输出和文件。
## 概要
```shell
tee [OPTION]... [FILE]...
```
## 主要用途
- 需要同时查看数据内容并输出到文件时使用。
## 参数
FILE(可选):要输出的文件,可以为一或多个。
## 选项
```shell
长选项与短选项等价
-a, --append 追加到文件中而不是覆盖。
-i, --ignore-interrupts 忽略中断信号(Ctrl+c中断操作无效)。
-p 诊断写入非管道的错误。
--output-error[=MODE] 设... | sec-knowleage |
# HALP (network 300)
###ENG
[PL](#pl-version)
In the task we get a [pcap file](transmission.pcap).
The file is from some VoIP call.
If we analyse the RTP streams and use VoIP feature of Wireshark to play the streams it can find, we will hear someone connecting to an automatic response machine, and then typing a number ... | sec-knowleage |
.\" Automatically generated by Pod::Man v1.37, Pod::Parser v1.13
.\"
.\" Standard preamble:
.\" ========================================================================
.de Sh \" Subsection heading
.br
.if t .Sp
.ne 5
.PP
\fB\\$1\fR
.PP
..
.de Sp \" Vertical space (when we can't use .PP)
.if t .sp .5v
.if n .sp
..
.de ... | sec-knowleage |
# 对于黑灰产行业的产业链分析
本篇主要整理互联网行业的黑灰产行业的各种产业链及推广模式。主要的思路是根据产业链的上中下游进行分层的整理:
- 上游 —— 攻击链
- 中游 —— 生产链
- 下游 —— 实施链
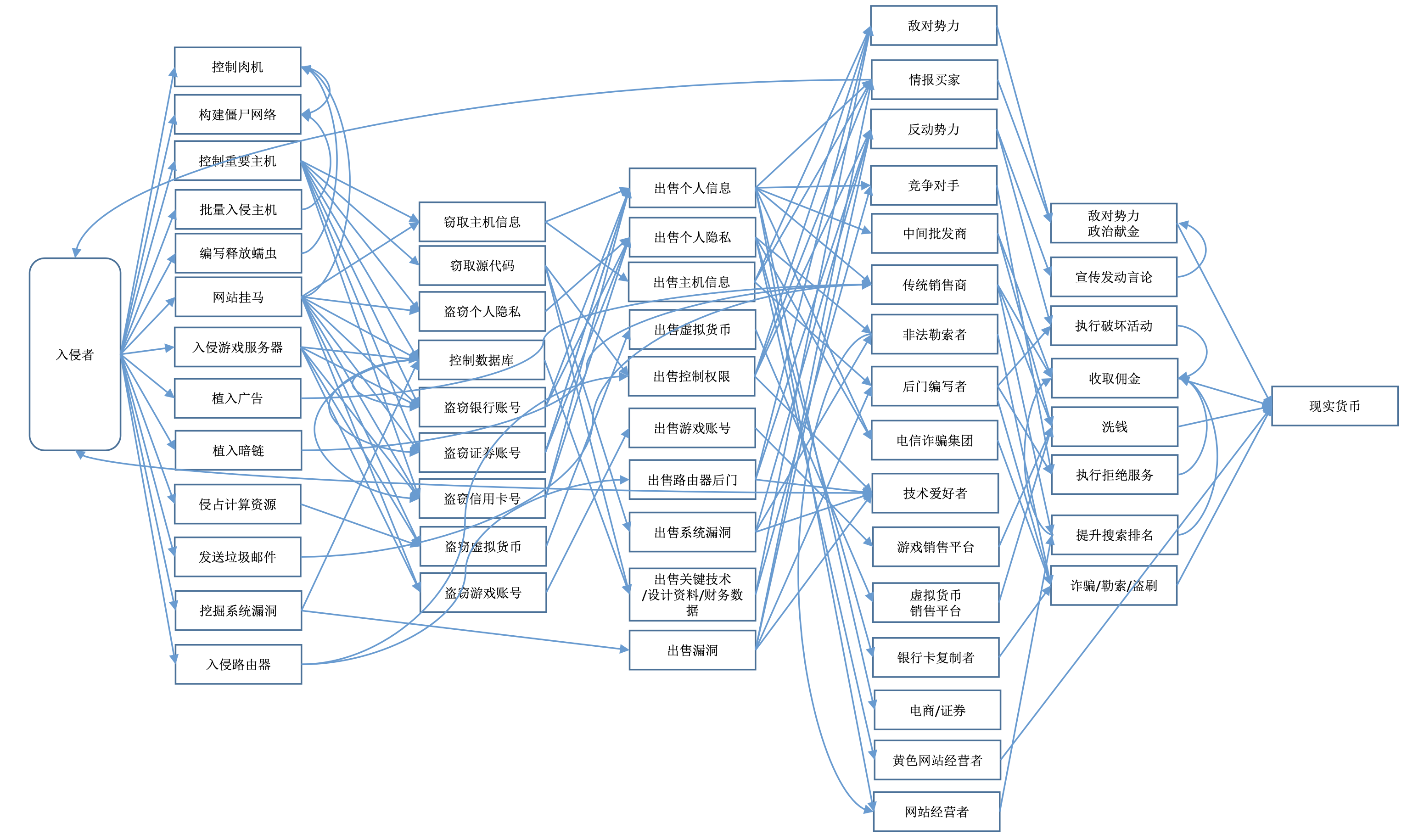
图:黑色产业链示意图
## 0. 产业链角色
在分析产业链时,首先,我们需要对参与其中的角色进行一个整理。以下是对黑灰产行业上中下游及相关角色的分析:
### 上游及相关角色
产业链上游根据中游和下游的需求,生产和提供各类**黑灰产资源**。主要提供“原材料”。... | sec-knowleage |
'\"
'\" Copyright (c) 1993 The Regents of the University of California.
'\" Copyright (c) 1994-1996 Sun Microsystems, Inc.
'\"
'\" See the file "license.terms" for information on usage and redistribution
'\" of this file, and for a DISCLAIMER OF ALL WARRANTIES.
'\"
'\" RCS: @(#) $Id: list.n,v 1.2 2003/11/24 05:09:59 b... | sec-knowleage |
# FTP
`FTP` ( `File Transfer Protocol` ,即文件传输协议)是 `TCP/IP` 协议组中的协议之一。 `FTP` 协议包括两个组成部分,其一为 `FTP` 服务器,其二为 `FTP` 客户端。其中 `FTP` 服务器用来存储文件,用户可以使用 `FTP` 客户端通过 `FTP` 协议访问位于 `FTP` 服务器上的资源。在开发网站的时候,通常利用 `FTP` 协议把网页或程序传到 `Web` 服务器上。此外,由于 `FTP` 传输效率非常高,在网络上传输大的文件时,一般也采用该协议。
默认情况下 `FTP` 协议使用 `TCP` 端口中的 `20` 和 `21` 这两个端口,其中 `20` 用于... | sec-knowleage |
# Contributing
> _A real community, however, exists only when its members interact in a meaningful way that deepens their understanding of each other and leads to learning._
If you would like to support this project, have an interesting idea how to improve the operation of this tool, or if you found some errors - for... | sec-knowleage |
# flag_shop
General Skills, 300 points
## Description:
> There's a flag shop selling stuff, can you buy a flag?
```c
#include <stdio.h>
#include <stdlib.h>
int main()
{
setbuf(stdout, NULL);
int con;
con = 0;
int account_balance = 1100;
while(con == 0){
printf("Welcome to the flag exchange\n... | sec-knowleage |
Subsets and Splits
Top 100 EPUB Books
This query retrieves a limited set of raw data entries that belong to the 'epub_books' category, offering only basic filtering without deeper insights.