Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 757 | labels stringlengths 4 664 | body stringlengths 3 261k | index stringclasses 10 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 232k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
334,877 | 24,443,102,998 | IssuesEvent | 2022-10-06 15:49:21 | JNU-econovation/econo-beep-server | https://api.github.com/repos/JNU-econovation/econo-beep-server | opened | 클래스 다이어그램 작성 및 리팩토링 대상 점검 | documentation | 프로젝트 클래스에 대한 클래스 다이어그램을 작성하면서 리팩토링 대상을 리스트화
- [ ] entity
- [ ] repository
- [ ] service
- [ ] dto
- [ ] controller | 1.0 | 클래스 다이어그램 작성 및 리팩토링 대상 점검 - 프로젝트 클래스에 대한 클래스 다이어그램을 작성하면서 리팩토링 대상을 리스트화
- [ ] entity
- [ ] repository
- [ ] service
- [ ] dto
- [ ] controller | non_defect | 클래스 다이어그램 작성 및 리팩토링 대상 점검 프로젝트 클래스에 대한 클래스 다이어그램을 작성하면서 리팩토링 대상을 리스트화 entity repository service dto controller | 0 |
47,557 | 13,056,245,025 | IssuesEvent | 2020-07-30 04:06:30 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | closed | gulliver-modules::reversefit test fails on SL5 32bit (Trac #747) | Migrated from Trac combo reconstruction defect |
```text
ERROR (I3FortyTwo): PLEASE INVESTIGATE (fortytwo.py:185 in Finish)
FATAL (I3FortyTwo): SOME CHECKS FAILED (fortytwo.py:186 in Finish)
ERROR (I3Module): <class 'fortytwo.I3FortyTwo'>_0000: Exception thrown (I3Module.cxx:113 in void I3Module::Do(void (I3Module::*)()))
Traceback (most recent call last):
File "/build/buildslave/foraii/quick_icerec_SL5/source/gulliver-modules/resources/scripts/reversefit.py", line 258, in ?
tray.Finish()
File "/build/buildslave/foraii/quick_icerec_SL5/source/gulliver-modules/resources/scripts/fortytwo.py", line 186, in Finish
icetray.logging.log_fatal("SOME CHECKS FAILED",unit=u42)
File "/build/buildslave/foraii/quick_icerec_SL5/build/lib/icecube/icetray/i3logging.py", line 150, in log_fatal
raise RuntimeError(message + " (in " + tb[2] + ")")
RuntimeError: SOME CHECKS FAILED (in Finish)
```
More details at: http://builds.icecube.wisc.edu/builders/quick_icerec_SL5/builds/1103/steps/test/logs/stdio
Migrated from https://code.icecube.wisc.edu/ticket/747
```json
{
"status": "closed",
"changetime": "2015-02-11T17:23:42",
"description": "{{{\nERROR (I3FortyTwo): PLEASE INVESTIGATE (fortytwo.py:185 in Finish)\nFATAL (I3FortyTwo): SOME CHECKS FAILED (fortytwo.py:186 in Finish)\nERROR (I3Module): <class 'fortytwo.I3FortyTwo'>_0000: Exception thrown (I3Module.cxx:113 in void I3Module::Do(void (I3Module::*)()))\nTraceback (most recent call last):\n File \"/build/buildslave/foraii/quick_icerec_SL5/source/gulliver-modules/resources/scripts/reversefit.py\", line 258, in ?\n tray.Finish()\n File \"/build/buildslave/foraii/quick_icerec_SL5/source/gulliver-modules/resources/scripts/fortytwo.py\", line 186, in Finish\n icetray.logging.log_fatal(\"SOME CHECKS FAILED\",unit=u42)\n File \"/build/buildslave/foraii/quick_icerec_SL5/build/lib/icecube/icetray/i3logging.py\", line 150, in log_fatal\n raise RuntimeError(message + \" (in \" + tb[2] + \")\")\nRuntimeError: SOME CHECKS FAILED (in Finish)\n}}}\n\nMore details at: http://builds.icecube.wisc.edu/builders/quick_icerec_SL5/builds/1103/steps/test/logs/stdio",
"reporter": "nega",
"cc": "dataclass@icecube.wisc.edu",
"resolution": "wontfix",
"_ts": "1423675422475856",
"component": "combo reconstruction",
"summary": "gulliver-modules::reversefit test fails on SL5 32bit",
"priority": "normal",
"keywords": "",
"time": "2014-09-05T21:21:19",
"milestone": "",
"owner": "boersma",
"type": "defect"
}
```
| 1.0 | gulliver-modules::reversefit test fails on SL5 32bit (Trac #747) -
```text
ERROR (I3FortyTwo): PLEASE INVESTIGATE (fortytwo.py:185 in Finish)
FATAL (I3FortyTwo): SOME CHECKS FAILED (fortytwo.py:186 in Finish)
ERROR (I3Module): <class 'fortytwo.I3FortyTwo'>_0000: Exception thrown (I3Module.cxx:113 in void I3Module::Do(void (I3Module::*)()))
Traceback (most recent call last):
File "/build/buildslave/foraii/quick_icerec_SL5/source/gulliver-modules/resources/scripts/reversefit.py", line 258, in ?
tray.Finish()
File "/build/buildslave/foraii/quick_icerec_SL5/source/gulliver-modules/resources/scripts/fortytwo.py", line 186, in Finish
icetray.logging.log_fatal("SOME CHECKS FAILED",unit=u42)
File "/build/buildslave/foraii/quick_icerec_SL5/build/lib/icecube/icetray/i3logging.py", line 150, in log_fatal
raise RuntimeError(message + " (in " + tb[2] + ")")
RuntimeError: SOME CHECKS FAILED (in Finish)
```
More details at: http://builds.icecube.wisc.edu/builders/quick_icerec_SL5/builds/1103/steps/test/logs/stdio
Migrated from https://code.icecube.wisc.edu/ticket/747
```json
{
"status": "closed",
"changetime": "2015-02-11T17:23:42",
"description": "{{{\nERROR (I3FortyTwo): PLEASE INVESTIGATE (fortytwo.py:185 in Finish)\nFATAL (I3FortyTwo): SOME CHECKS FAILED (fortytwo.py:186 in Finish)\nERROR (I3Module): <class 'fortytwo.I3FortyTwo'>_0000: Exception thrown (I3Module.cxx:113 in void I3Module::Do(void (I3Module::*)()))\nTraceback (most recent call last):\n File \"/build/buildslave/foraii/quick_icerec_SL5/source/gulliver-modules/resources/scripts/reversefit.py\", line 258, in ?\n tray.Finish()\n File \"/build/buildslave/foraii/quick_icerec_SL5/source/gulliver-modules/resources/scripts/fortytwo.py\", line 186, in Finish\n icetray.logging.log_fatal(\"SOME CHECKS FAILED\",unit=u42)\n File \"/build/buildslave/foraii/quick_icerec_SL5/build/lib/icecube/icetray/i3logging.py\", line 150, in log_fatal\n raise RuntimeError(message + \" (in \" + tb[2] + \")\")\nRuntimeError: SOME CHECKS FAILED (in Finish)\n}}}\n\nMore details at: http://builds.icecube.wisc.edu/builders/quick_icerec_SL5/builds/1103/steps/test/logs/stdio",
"reporter": "nega",
"cc": "dataclass@icecube.wisc.edu",
"resolution": "wontfix",
"_ts": "1423675422475856",
"component": "combo reconstruction",
"summary": "gulliver-modules::reversefit test fails on SL5 32bit",
"priority": "normal",
"keywords": "",
"time": "2014-09-05T21:21:19",
"milestone": "",
"owner": "boersma",
"type": "defect"
}
```
| defect | gulliver modules reversefit test fails on trac text error please investigate fortytwo py in finish fatal some checks failed fortytwo py in finish error exception thrown cxx in void do void traceback most recent call last file build buildslave foraii quick icerec source gulliver modules resources scripts reversefit py line in tray finish file build buildslave foraii quick icerec source gulliver modules resources scripts fortytwo py line in finish icetray logging log fatal some checks failed unit file build buildslave foraii quick icerec build lib icecube icetray py line in log fatal raise runtimeerror message in tb runtimeerror some checks failed in finish more details at migrated from json status closed changetime description nerror please investigate fortytwo py in finish nfatal some checks failed fortytwo py in finish nerror exception thrown cxx in void do void ntraceback most recent call last n file build buildslave foraii quick icerec source gulliver modules resources scripts reversefit py line in n tray finish n file build buildslave foraii quick icerec source gulliver modules resources scripts fortytwo py line in finish n icetray logging log fatal some checks failed unit n file build buildslave foraii quick icerec build lib icecube icetray py line in log fatal n raise runtimeerror message in tb nruntimeerror some checks failed in finish n n nmore details at reporter nega cc dataclass icecube wisc edu resolution wontfix ts component combo reconstruction summary gulliver modules reversefit test fails on priority normal keywords time milestone owner boersma type defect | 1 |
709,323 | 24,373,824,802 | IssuesEvent | 2022-10-03 22:00:02 | fecgov/openFEC | https://api.github.com/repos/fecgov/openFEC | closed | Dev API CircleCI builds failing | Needs refinement High priority | ### Summary
Dev API CircleCI builds are failing on the `celery-beat` deployment stage. Error messages include:
`ERR Failed to compress build artifacts: exit status 2`
`ERR Failed to stage build: staging failed`
### Completion criteria
- [ ] Failing Dev API CircleCi builds are fixed | 1.0 | Dev API CircleCI builds failing - ### Summary
Dev API CircleCI builds are failing on the `celery-beat` deployment stage. Error messages include:
`ERR Failed to compress build artifacts: exit status 2`
`ERR Failed to stage build: staging failed`
### Completion criteria
- [ ] Failing Dev API CircleCi builds are fixed | non_defect | dev api circleci builds failing summary dev api circleci builds are failing on the celery beat deployment stage error messages include err failed to compress build artifacts exit status err failed to stage build staging failed completion criteria failing dev api circleci builds are fixed | 0 |
107,355 | 16,758,608,898 | IssuesEvent | 2021-06-13 10:14:14 | semarmendemx/vulnado | https://api.github.com/repos/semarmendemx/vulnado | closed | CVE-2019-20330 (High) detected in jackson-databind-2.9.8.jar - autoclosed | security vulnerability | ## CVE-2019-20330 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: vulnado/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- jjwt-jackson-0.10.5.jar (Root Library)
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/semarmendemx/vulnado/commits/32814c7fcfe30a55a8d0148cfe4388bdc8141fe8">32814c7fcfe30a55a8d0148cfe4388bdc8141fe8</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.2 lacks certain net.sf.ehcache blocking.
<p>Publish Date: 2020-01-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-20330>CVE-2019-20330</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2526">https://github.com/FasterXML/jackson-databind/issues/2526</a></p>
<p>Release Date: 2020-01-03</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.7.9.7,2.8.11.5,2.9.10.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-20330 (High) detected in jackson-databind-2.9.8.jar - autoclosed - ## CVE-2019-20330 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: vulnado/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- jjwt-jackson-0.10.5.jar (Root Library)
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/semarmendemx/vulnado/commits/32814c7fcfe30a55a8d0148cfe4388bdc8141fe8">32814c7fcfe30a55a8d0148cfe4388bdc8141fe8</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.2 lacks certain net.sf.ehcache blocking.
<p>Publish Date: 2020-01-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-20330>CVE-2019-20330</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2526">https://github.com/FasterXML/jackson-databind/issues/2526</a></p>
<p>Release Date: 2020-01-03</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.7.9.7,2.8.11.5,2.9.10.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_defect | cve high detected in jackson databind jar autoclosed cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file vulnado pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy jjwt jackson jar root library x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before lacks certain net sf ehcache blocking publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with whitesource | 0 |
67,206 | 20,961,583,621 | IssuesEvent | 2022-03-27 21:43:54 | abedmaatalla/foursquared | https://api.github.com/repos/abedmaatalla/foursquared | closed | Favorite/Daily checkins tab feature request | Priority-Medium Type-Defect auto-migrated | ```
Hi,
what do you think about adding additional tab or menu entry for may favorite
places? I could mark some places as my favorite. Then I could choose to
check-in in them faster.
```
Original issue reported on code.google.com by `Coffy...@gmail.com` on 15 Feb 2011 at 1:29
| 1.0 | Favorite/Daily checkins tab feature request - ```
Hi,
what do you think about adding additional tab or menu entry for may favorite
places? I could mark some places as my favorite. Then I could choose to
check-in in them faster.
```
Original issue reported on code.google.com by `Coffy...@gmail.com` on 15 Feb 2011 at 1:29
| defect | favorite daily checkins tab feature request hi what do you think about adding additional tab or menu entry for may favorite places i could mark some places as my favorite then i could choose to check in in them faster original issue reported on code google com by coffy gmail com on feb at | 1 |
60,437 | 17,023,425,238 | IssuesEvent | 2021-07-03 01:57:59 | tomhughes/trac-tickets | https://api.github.com/repos/tomhughes/trac-tickets | closed | Missing QTransform in TrackPoint.cpp line 151 | Component: merkaartor Priority: blocker Resolution: fixed Type: defect | **[Submitted to the original trac issue database at 10.01am, Monday, 15th June 2009]**
The current svn doesn't build because of that error
Maps/TrackPoint.cpp:151: erreur: prototype for void TrackPoint::draw(QPainter&, const Projection&) does not match any in class TrackPoint
Maps/TrackPoint.h:33: erreur: candidate is: virtual void TrackPoint::draw(QPainter&, const Projection&, const QTransform&)
| 1.0 | Missing QTransform in TrackPoint.cpp line 151 - **[Submitted to the original trac issue database at 10.01am, Monday, 15th June 2009]**
The current svn doesn't build because of that error
Maps/TrackPoint.cpp:151: erreur: prototype for void TrackPoint::draw(QPainter&, const Projection&) does not match any in class TrackPoint
Maps/TrackPoint.h:33: erreur: candidate is: virtual void TrackPoint::draw(QPainter&, const Projection&, const QTransform&)
| defect | missing qtransform in trackpoint cpp line the current svn doesn t build because of that error maps trackpoint cpp erreur prototype for void trackpoint draw qpainter const projection does not match any in class trackpoint maps trackpoint h erreur candidate is virtual void trackpoint draw qpainter const projection const qtransform | 1 |
280,447 | 30,826,114,701 | IssuesEvent | 2023-08-01 20:12:45 | GHCbflam1/WebGoat | https://api.github.com/repos/GHCbflam1/WebGoat | closed | hsqldb-2.5.2.jar: 1 vulnerabilities (highest severity is: 9.8) - autoclosed | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>hsqldb-2.5.2.jar</b></p></summary>
<p>HSQLDB - Lightweight 100% Java SQL Database Engine</p>
<p>Library home page: <a href="http://hsqldb.org">http://hsqldb.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /m2/repository/org/hsqldb/hsqldb/2.5.2/hsqldb-2.5.2.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/GHCbflam1/WebGoat/commit/2b69e0de79c729ec6485508a75f09b16e218921a">2b69e0de79c729ec6485508a75f09b16e218921a</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (hsqldb version) | Fix PR available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-41853](https://www.mend.io/vulnerability-database/CVE-2022-41853) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | hsqldb-2.5.2.jar | Direct | N/A | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2022-41853</summary>
### Vulnerable Library - <b>hsqldb-2.5.2.jar</b></p>
<p>HSQLDB - Lightweight 100% Java SQL Database Engine</p>
<p>Library home page: <a href="http://hsqldb.org">http://hsqldb.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /m2/repository/org/hsqldb/hsqldb/2.5.2/hsqldb-2.5.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **hsqldb-2.5.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/GHCbflam1/WebGoat/commit/2b69e0de79c729ec6485508a75f09b16e218921a">2b69e0de79c729ec6485508a75f09b16e218921a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Those using java.sql.Statement or java.sql.PreparedStatement in hsqldb (HyperSQL DataBase) to process untrusted input may be vulnerable to a remote code execution attack. By default it is allowed to call any static method of any Java class in the classpath resulting in code execution. The issue can be prevented by updating to 2.7.1 or by setting the system property "hsqldb.method_class_names" to classes which are allowed to be called. For example, System.setProperty("hsqldb.method_class_names", "abc") or Java argument -Dhsqldb.method_class_names="abc" can be used. From version 2.7.1 all classes by default are not accessible except those in java.lang.Math and need to be manually enabled.
<p>Publish Date: 2022-10-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41853>CVE-2022-41853</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | True | hsqldb-2.5.2.jar: 1 vulnerabilities (highest severity is: 9.8) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>hsqldb-2.5.2.jar</b></p></summary>
<p>HSQLDB - Lightweight 100% Java SQL Database Engine</p>
<p>Library home page: <a href="http://hsqldb.org">http://hsqldb.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /m2/repository/org/hsqldb/hsqldb/2.5.2/hsqldb-2.5.2.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/GHCbflam1/WebGoat/commit/2b69e0de79c729ec6485508a75f09b16e218921a">2b69e0de79c729ec6485508a75f09b16e218921a</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (hsqldb version) | Fix PR available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-41853](https://www.mend.io/vulnerability-database/CVE-2022-41853) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | hsqldb-2.5.2.jar | Direct | N/A | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2022-41853</summary>
### Vulnerable Library - <b>hsqldb-2.5.2.jar</b></p>
<p>HSQLDB - Lightweight 100% Java SQL Database Engine</p>
<p>Library home page: <a href="http://hsqldb.org">http://hsqldb.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /m2/repository/org/hsqldb/hsqldb/2.5.2/hsqldb-2.5.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **hsqldb-2.5.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/GHCbflam1/WebGoat/commit/2b69e0de79c729ec6485508a75f09b16e218921a">2b69e0de79c729ec6485508a75f09b16e218921a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Those using java.sql.Statement or java.sql.PreparedStatement in hsqldb (HyperSQL DataBase) to process untrusted input may be vulnerable to a remote code execution attack. By default it is allowed to call any static method of any Java class in the classpath resulting in code execution. The issue can be prevented by updating to 2.7.1 or by setting the system property "hsqldb.method_class_names" to classes which are allowed to be called. For example, System.setProperty("hsqldb.method_class_names", "abc") or Java argument -Dhsqldb.method_class_names="abc" can be used. From version 2.7.1 all classes by default are not accessible except those in java.lang.Math and need to be manually enabled.
<p>Publish Date: 2022-10-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41853>CVE-2022-41853</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | non_defect | hsqldb jar vulnerabilities highest severity is autoclosed vulnerable library hsqldb jar hsqldb lightweight java sql database engine library home page a href path to dependency file pom xml path to vulnerable library repository org hsqldb hsqldb hsqldb jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in hsqldb version fix pr available critical hsqldb jar direct n a details cve vulnerable library hsqldb jar hsqldb lightweight java sql database engine library home page a href path to dependency file pom xml path to vulnerable library repository org hsqldb hsqldb hsqldb jar dependency hierarchy x hsqldb jar vulnerable library found in head commit a href found in base branch main vulnerability details those using java sql statement or java sql preparedstatement in hsqldb hypersql database to process untrusted input may be vulnerable to a remote code execution attack by default it is allowed to call any static method of any java class in the classpath resulting in code execution the issue can be prevented by updating to or by setting the system property hsqldb method class names to classes which are allowed to be called for example system setproperty hsqldb method class names abc or java argument dhsqldb method class names abc can be used from version all classes by default are not accessible except those in java lang math and need to be manually enabled publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue | 0 |
74,601 | 25,203,462,744 | IssuesEvent | 2022-11-13 11:55:23 | micahmo/WgServerforWindows | https://api.github.com/repos/micahmo/WgServerforWindows | closed | Can't enable internet sharing after enabling NAT | not-a-defect | following the setup steps once NAT is enabled, I cannot enable internet sharing or persistent sharing, both buttons are greyed out. I can enable internet sharing manually by opening the network connections properties. reopening the Wg Server app shows sharing is enabled but not persistent.
I have gone into regedit and changed HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedAccess\EnableRebootPersistConnection from 0 to 1 and changed "Internet Connection Sharing" in services from manual to automatic. so far with a restart of windows it all seems to be working on a remote client, but the app still shows persistent sharing is disabled with the button greyed out.
This is on the most recent win 10 updates on 22H2. is there a manual setting I am missing or can the app be updated to allow the buttons to work?
| 1.0 | Can't enable internet sharing after enabling NAT - following the setup steps once NAT is enabled, I cannot enable internet sharing or persistent sharing, both buttons are greyed out. I can enable internet sharing manually by opening the network connections properties. reopening the Wg Server app shows sharing is enabled but not persistent.
I have gone into regedit and changed HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedAccess\EnableRebootPersistConnection from 0 to 1 and changed "Internet Connection Sharing" in services from manual to automatic. so far with a restart of windows it all seems to be working on a remote client, but the app still shows persistent sharing is disabled with the button greyed out.
This is on the most recent win 10 updates on 22H2. is there a manual setting I am missing or can the app be updated to allow the buttons to work?
| defect | can t enable internet sharing after enabling nat following the setup steps once nat is enabled i cannot enable internet sharing or persistent sharing both buttons are greyed out i can enable internet sharing manually by opening the network connections properties reopening the wg server app shows sharing is enabled but not persistent i have gone into regedit and changed hkey local machine software microsoft windows currentversion sharedaccess enablerebootpersistconnection from to and changed internet connection sharing in services from manual to automatic so far with a restart of windows it all seems to be working on a remote client but the app still shows persistent sharing is disabled with the button greyed out this is on the most recent win updates on is there a manual setting i am missing or can the app be updated to allow the buttons to work | 1 |
2,291 | 3,374,384,460 | IssuesEvent | 2015-11-24 12:47:08 | poppyGP/poppyGP | https://api.github.com/repos/poppyGP/poppyGP | opened | [PAGE LAYOUT] Viewport Sizes and Devices | 0.5: Performance 0.6: UI/UX 0.7: Layout 1.2: Front-End 2.1: AngularJS 2.2: CSS3 2.3: Sass 2.4: HTML 2.5: KiwiIRC | Objective
---------
Detail & structure all layout components to determine responsiveness and placement.
Table (WIP)
-----------
| Viewport/Device | Sass | Wrappers | Schedule |
| :-------------- | :-----: | :-------- | :-------- |
| Mobile, port | `mo-pt` | Stacked | Text Line
| Mobile, land | `mo-ls` | Inline | Text Line
| Phablet, port | `ph-pt` | Stacked | Text Line
| Phablet, land | `ph-ls` | Inline | Icon
| Tablet, port | `tb-pt` | Stacked | Icon
| Tablet, land | `tb-ls` | Inline | Icon
| Screen, xsmall | `sc-xs` | Inline | Icon
| Screen, small | `sc-sm` | Inline | Icon Row
| Screen, medium | `sc-md` | Inline | Icon Row
| Screen, large | `sc-lg` | Inline | Icon Row
| Screen, xlarge | `sc-xl` | Inline | Icon Row
Components
----------
- `gp-toolbar` - top toolbar
- `gp-canvas` - main container
- `gp-video`
- `gp-panel`
- `gp-infobar` | True | [PAGE LAYOUT] Viewport Sizes and Devices - Objective
---------
Detail & structure all layout components to determine responsiveness and placement.
Table (WIP)
-----------
| Viewport/Device | Sass | Wrappers | Schedule |
| :-------------- | :-----: | :-------- | :-------- |
| Mobile, port | `mo-pt` | Stacked | Text Line
| Mobile, land | `mo-ls` | Inline | Text Line
| Phablet, port | `ph-pt` | Stacked | Text Line
| Phablet, land | `ph-ls` | Inline | Icon
| Tablet, port | `tb-pt` | Stacked | Icon
| Tablet, land | `tb-ls` | Inline | Icon
| Screen, xsmall | `sc-xs` | Inline | Icon
| Screen, small | `sc-sm` | Inline | Icon Row
| Screen, medium | `sc-md` | Inline | Icon Row
| Screen, large | `sc-lg` | Inline | Icon Row
| Screen, xlarge | `sc-xl` | Inline | Icon Row
Components
----------
- `gp-toolbar` - top toolbar
- `gp-canvas` - main container
- `gp-video`
- `gp-panel`
- `gp-infobar` | non_defect | viewport sizes and devices objective detail structure all layout components to determine responsiveness and placement table wip viewport device sass wrappers schedule mobile port mo pt stacked text line mobile land mo ls inline text line phablet port ph pt stacked text line phablet land ph ls inline icon tablet port tb pt stacked icon tablet land tb ls inline icon screen xsmall sc xs inline icon screen small sc sm inline icon row screen medium sc md inline icon row screen large sc lg inline icon row screen xlarge sc xl inline icon row components gp toolbar top toolbar gp canvas main container gp video gp panel gp infobar | 0 |
23,483 | 3,833,099,132 | IssuesEvent | 2016-04-01 00:50:02 | klaroskuro1809/webslayer | https://api.github.com/repos/klaroskuro1809/webslayer | closed | Memory Leak | auto-migrated Priority-High Type-Defect | ```
What steps will reproduce the problem?
1. using payload and a range from 000000 to 999999
2.
3.
What is the expected output? What do you see instead?
it gets very slow and hangs.
increase memory usage above 2GB ram just for its process
What version of the product are you using? On what operating system?
beta on windows xp sp3
Please provide any additional information below.
```
Original issue reported on code.google.com by `alem...@gmail.com` on 21 Sep 2009 at 5:42 | 1.0 | Memory Leak - ```
What steps will reproduce the problem?
1. using payload and a range from 000000 to 999999
2.
3.
What is the expected output? What do you see instead?
it gets very slow and hangs.
increase memory usage above 2GB ram just for its process
What version of the product are you using? On what operating system?
beta on windows xp sp3
Please provide any additional information below.
```
Original issue reported on code.google.com by `alem...@gmail.com` on 21 Sep 2009 at 5:42 | defect | memory leak what steps will reproduce the problem using payload and a range from to what is the expected output what do you see instead it gets very slow and hangs increase memory usage above ram just for its process what version of the product are you using on what operating system beta on windows xp please provide any additional information below original issue reported on code google com by alem gmail com on sep at | 1 |
761,175 | 26,670,562,269 | IssuesEvent | 2023-01-26 09:54:26 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | auth0.openai.com - see bug description | priority-normal browser-fenix engine-gecko android13 | <!-- @browser: Firefox Mobile 111.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 13; Mobile; rv:109.0) Gecko/111.0 Firefox/111.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/117387 -->
<!-- @extra_labels: browser-fenix -->
**URL**: https://auth0.openai.com/u/login/identifier?state=hKFo2SBBUVpKM2YydVVGX1pYR25BWGNhbmhWSzBIaTR2UmlodqFur3VuaXZlcnNhbC1sb2dpbqN0aWTZIG9tbFRWNVZoR3Q4NFhJYml3NlQ5QkxUaU1vM0dkLXc1o2NpZNkgVGRKSWNiZTE2V29USHROOTVueXl3aDVFNHlPbzZJdEc
**Browser / Version**: Firefox Mobile 111.0
**Operating System**: Android 13
**Tested Another Browser**: Yes Chrome
**Problem type**: Something else
**Description**: can't login using google
**Steps to Reproduce**:
Click use google to sign in and nothing happens
<details>
<summary>View the screenshot</summary>
<img alt="Screenshot" src="https://webcompat.com/uploads/2023/1/f26f1992-27b3-4e3f-8daf-8c95e0d77986.jpeg">
</details>
<details>
<summary>Browser Configuration</summary>
<ul>
<li>gfx.webrender.all: false</li><li>gfx.webrender.blob-images: true</li><li>gfx.webrender.enabled: false</li><li>image.mem.shared: true</li><li>buildID: 20230125094200</li><li>channel: nightly</li><li>hasTouchScreen: true</li><li>mixed active content blocked: false</li><li>mixed passive content blocked: false</li><li>tracking content blocked: false</li>
</ul>
</details>
[View console log messages](https://webcompat.com/console_logs/2023/1/7171534d-43d9-4044-b68f-0b2e3013f7f9)
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | auth0.openai.com - see bug description - <!-- @browser: Firefox Mobile 111.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 13; Mobile; rv:109.0) Gecko/111.0 Firefox/111.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/117387 -->
<!-- @extra_labels: browser-fenix -->
**URL**: https://auth0.openai.com/u/login/identifier?state=hKFo2SBBUVpKM2YydVVGX1pYR25BWGNhbmhWSzBIaTR2UmlodqFur3VuaXZlcnNhbC1sb2dpbqN0aWTZIG9tbFRWNVZoR3Q4NFhJYml3NlQ5QkxUaU1vM0dkLXc1o2NpZNkgVGRKSWNiZTE2V29USHROOTVueXl3aDVFNHlPbzZJdEc
**Browser / Version**: Firefox Mobile 111.0
**Operating System**: Android 13
**Tested Another Browser**: Yes Chrome
**Problem type**: Something else
**Description**: can't login using google
**Steps to Reproduce**:
Click use google to sign in and nothing happens
<details>
<summary>View the screenshot</summary>
<img alt="Screenshot" src="https://webcompat.com/uploads/2023/1/f26f1992-27b3-4e3f-8daf-8c95e0d77986.jpeg">
</details>
<details>
<summary>Browser Configuration</summary>
<ul>
<li>gfx.webrender.all: false</li><li>gfx.webrender.blob-images: true</li><li>gfx.webrender.enabled: false</li><li>image.mem.shared: true</li><li>buildID: 20230125094200</li><li>channel: nightly</li><li>hasTouchScreen: true</li><li>mixed active content blocked: false</li><li>mixed passive content blocked: false</li><li>tracking content blocked: false</li>
</ul>
</details>
[View console log messages](https://webcompat.com/console_logs/2023/1/7171534d-43d9-4044-b68f-0b2e3013f7f9)
_From [webcompat.com](https://webcompat.com/) with ❤️_ | non_defect | openai com see bug description url browser version firefox mobile operating system android tested another browser yes chrome problem type something else description can t login using google steps to reproduce click use google to sign in and nothing happens view the screenshot img alt screenshot src browser configuration gfx webrender all false gfx webrender blob images true gfx webrender enabled false image mem shared true buildid channel nightly hastouchscreen true mixed active content blocked false mixed passive content blocked false tracking content blocked false from with ❤️ | 0 |
198,394 | 22,636,547,695 | IssuesEvent | 2022-06-30 19:37:33 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Optimize `security` page load bundle | good first issue chore Team:Security | The work to introduce user profile support has nearly doubled the size of our page load bundle (https://github.com/elastic/kibana/pull/132522). We are just barely under the `100kb` suggested limit after these changes, so we should work to bring this down to a more comfortable level.
<img width="598" alt="CleanShot 2022-06-01 at 14 04 35@2x" src="https://user-images.githubusercontent.com/3493255/171472608-7457a24d-ff37-472e-b147-73f0ca2aa0da.png">
See https://www.elastic.co/guide/en/kibana/master/ci-metrics.html#ci-metric-resolving-overages for instructions on how to resolve bundle overages. | True | Optimize `security` page load bundle - The work to introduce user profile support has nearly doubled the size of our page load bundle (https://github.com/elastic/kibana/pull/132522). We are just barely under the `100kb` suggested limit after these changes, so we should work to bring this down to a more comfortable level.
<img width="598" alt="CleanShot 2022-06-01 at 14 04 35@2x" src="https://user-images.githubusercontent.com/3493255/171472608-7457a24d-ff37-472e-b147-73f0ca2aa0da.png">
See https://www.elastic.co/guide/en/kibana/master/ci-metrics.html#ci-metric-resolving-overages for instructions on how to resolve bundle overages. | non_defect | optimize security page load bundle the work to introduce user profile support has nearly doubled the size of our page load bundle we are just barely under the suggested limit after these changes so we should work to bring this down to a more comfortable level img width alt cleanshot at src see for instructions on how to resolve bundle overages | 0 |
54,993 | 3,071,777,298 | IssuesEvent | 2015-08-19 13:59:15 | RobotiumTech/robotium | https://api.github.com/repos/RobotiumTech/robotium | closed | I would like to get the ID of the item in the menu | bug imported invalid Priority-Medium | _From [sergio.p...@gmail.com](https://code.google.com/u/110077335906614796847/) on January 31, 2011 01:18:50_
What steps will reproduce the problem? 1.I would like to get the ID of the item in the menu 2. 3. What is the expected output? What do you see instead? What version of the product are you using? On what operating system? 2.1 with windows Please provide any additional information below. I open the menu with the statement solo.sendkey (solo.menu), but I can not get the references of the buttons in the menu.
I would like to save in a Arrey the IDs of menu buttons.
I hope someone can help me.
Thanks.
_Original issue: http://code.google.com/p/robotium/issues/detail?id=60_ | 1.0 | I would like to get the ID of the item in the menu - _From [sergio.p...@gmail.com](https://code.google.com/u/110077335906614796847/) on January 31, 2011 01:18:50_
What steps will reproduce the problem? 1.I would like to get the ID of the item in the menu 2. 3. What is the expected output? What do you see instead? What version of the product are you using? On what operating system? 2.1 with windows Please provide any additional information below. I open the menu with the statement solo.sendkey (solo.menu), but I can not get the references of the buttons in the menu.
I would like to save in a Arrey the IDs of menu buttons.
I hope someone can help me.
Thanks.
_Original issue: http://code.google.com/p/robotium/issues/detail?id=60_ | non_defect | i would like to get the id of the item in the menu from on january what steps will reproduce the problem i would like to get the id of the item in the menu what is the expected output what do you see instead what version of the product are you using on what operating system with windows please provide any additional information below i open the menu with the statement solo sendkey solo menu but i can not get the references of the buttons in the menu i would like to save in a arrey the ids of menu buttons i hope someone can help me thanks original issue | 0 |
123,489 | 10,270,437,474 | IssuesEvent | 2019-08-23 11:37:54 | mecoFarid/squeezeloader | https://api.github.com/repos/mecoFarid/squeezeloader | opened | Test on devices below API 16 (above 14) | add test | Since minimum SDK version is 14. The library should be tested on devices with minimum SDK version 14 | 1.0 | Test on devices below API 16 (above 14) - Since minimum SDK version is 14. The library should be tested on devices with minimum SDK version 14 | non_defect | test on devices below api above since minimum sdk version is the library should be tested on devices with minimum sdk version | 0 |
49,950 | 13,187,299,173 | IssuesEvent | 2020-08-13 02:58:25 | icecube-trac/tix3 | https://api.github.com/repos/icecube-trac/tix3 | opened | [MuonGun] Hidden overloaded virtual function in pybingins (Trac #2362) | Incomplete Migration Migrated from Trac combo simulation defect | <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/2362">https://code.icecube.wisc.edu/ticket/2362</a>, reported by kjmeagher and owned by jvansanten</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2020-06-24T12:31:42",
"description": "Clang gives me this warning:\n{{{\n[297/1701] Building CXX object MuonGun/CMakeFiles/MuonGun-pybindings.dir/private/pybindings/EnergyDistribution.cxx.o\n/Users/kmeagher/icecube/combo/src/MuonGun/private/pybindings/EnergyDistribution.cxx:22:17: warning: 'I3MuonGun::PyEnergyDistribution::GetLog' hides overloaded virtual function [-Woverloaded-virtual]\n virtual double GetLog(double depth, double cos_theta,\n ^\n/Users/kmeagher/icecube/combo/src/MuonGun/public/MuonGun/EnergyDistribution.h:50:17: note: hidden overloaded virtual function 'I3MuonGun::EnergyDistribution::GetLog' declared here: type mismatch at 5th parameter ('I3MuonGun::EnergyDistribution::log_value' vs 'double')\n virtual double GetLog(double depth, double cos_theta,\n ^\n1 warning generated.\n\n}}}\nThe problem is the 5th parameter which is of type `log_value` in the header but type `double` in the pybindings file ",
"reporter": "kjmeagher",
"cc": "",
"resolution": "fixed",
"_ts": "1593001902142004",
"component": "combo simulation",
"summary": "[MuonGun] Hidden overloaded virtual function in pybingins",
"priority": "normal",
"keywords": "",
"time": "2019-10-04T16:16:57",
"milestone": "Autumnal Equinox 2020",
"owner": "jvansanten",
"type": "defect"
}
```
</p>
</details>
| 1.0 | [MuonGun] Hidden overloaded virtual function in pybingins (Trac #2362) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/2362">https://code.icecube.wisc.edu/ticket/2362</a>, reported by kjmeagher and owned by jvansanten</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2020-06-24T12:31:42",
"description": "Clang gives me this warning:\n{{{\n[297/1701] Building CXX object MuonGun/CMakeFiles/MuonGun-pybindings.dir/private/pybindings/EnergyDistribution.cxx.o\n/Users/kmeagher/icecube/combo/src/MuonGun/private/pybindings/EnergyDistribution.cxx:22:17: warning: 'I3MuonGun::PyEnergyDistribution::GetLog' hides overloaded virtual function [-Woverloaded-virtual]\n virtual double GetLog(double depth, double cos_theta,\n ^\n/Users/kmeagher/icecube/combo/src/MuonGun/public/MuonGun/EnergyDistribution.h:50:17: note: hidden overloaded virtual function 'I3MuonGun::EnergyDistribution::GetLog' declared here: type mismatch at 5th parameter ('I3MuonGun::EnergyDistribution::log_value' vs 'double')\n virtual double GetLog(double depth, double cos_theta,\n ^\n1 warning generated.\n\n}}}\nThe problem is the 5th parameter which is of type `log_value` in the header but type `double` in the pybindings file ",
"reporter": "kjmeagher",
"cc": "",
"resolution": "fixed",
"_ts": "1593001902142004",
"component": "combo simulation",
"summary": "[MuonGun] Hidden overloaded virtual function in pybingins",
"priority": "normal",
"keywords": "",
"time": "2019-10-04T16:16:57",
"milestone": "Autumnal Equinox 2020",
"owner": "jvansanten",
"type": "defect"
}
```
</p>
</details>
| defect | hidden overloaded virtual function in pybingins trac migrated from json status closed changetime description clang gives me this warning n n building cxx object muongun cmakefiles muongun pybindings dir private pybindings energydistribution cxx o n users kmeagher icecube combo src muongun private pybindings energydistribution cxx warning pyenergydistribution getlog hides overloaded virtual function n virtual double getlog double depth double cos theta n n users kmeagher icecube combo src muongun public muongun energydistribution h note hidden overloaded virtual function energydistribution getlog declared here type mismatch at parameter energydistribution log value vs double n virtual double getlog double depth double cos theta n warning generated n n nthe problem is the parameter which is of type log value in the header but type double in the pybindings file reporter kjmeagher cc resolution fixed ts component combo simulation summary hidden overloaded virtual function in pybingins priority normal keywords time milestone autumnal equinox owner jvansanten type defect | 1 |
43,045 | 11,453,136,396 | IssuesEvent | 2020-02-06 14:54:28 | carbon-design-system/ibm-security | https://api.github.com/repos/carbon-design-system/ibm-security | closed | SummaryCardBatchActions - buttons in tab order even when they appear "hidden" | Defect released on @canary severity 3 | ## Bug - summary card batch action buttons are always in tab order, even when hidden
**Expected behavior -**
The batch actions toolbar for the `SummaryCardContainer` (called `SummaryCardBatchActions`) should not be interactive when it is "hidden" from view. You shouldn't be able to tab those hidden batch actions buttons.
**Actual behavior -**
The batch actions buttons in `SummaryCardBatchActions` are in the tab order even when they appear "hidden"
### Steps for reproducing
Go the storybook and see that you can tab to "hidden" batch actions buttons: https://ibm-security.carbondesignsystem.com/?path=/story/patterns-summarycard--multiselect | 1.0 | SummaryCardBatchActions - buttons in tab order even when they appear "hidden" - ## Bug - summary card batch action buttons are always in tab order, even when hidden
**Expected behavior -**
The batch actions toolbar for the `SummaryCardContainer` (called `SummaryCardBatchActions`) should not be interactive when it is "hidden" from view. You shouldn't be able to tab those hidden batch actions buttons.
**Actual behavior -**
The batch actions buttons in `SummaryCardBatchActions` are in the tab order even when they appear "hidden"
### Steps for reproducing
Go the storybook and see that you can tab to "hidden" batch actions buttons: https://ibm-security.carbondesignsystem.com/?path=/story/patterns-summarycard--multiselect | defect | summarycardbatchactions buttons in tab order even when they appear hidden bug summary card batch action buttons are always in tab order even when hidden expected behavior the batch actions toolbar for the summarycardcontainer called summarycardbatchactions should not be interactive when it is hidden from view you shouldn t be able to tab those hidden batch actions buttons actual behavior the batch actions buttons in summarycardbatchactions are in the tab order even when they appear hidden steps for reproducing go the storybook and see that you can tab to hidden batch actions buttons | 1 |
264,404 | 23,116,430,076 | IssuesEvent | 2022-07-27 17:07:26 | microsoft/vscode | https://api.github.com/repos/microsoft/vscode | closed | Test: Shell integration manual install | testplan-item | Refs: #153921
- [x] macOS @tanhakabir
- [x] linux @deepak1556
- [x] windows @hediet
- [x] WSL @joyceerhl (or any remote)
Complexity: 3
Authors: @Tyriar, @meganrogge
Roles: Developer, Engineering Manager
[Create Issue](https://github.com/microsoft/vscode/issues/new?body=Testing+%23156001%0A%0A&assignees=Tyriar,meganrogge)
---
Shell integration should be activated manually for the original shell launched in the terminal, but not in sub-shells. To workaround this you can manually install shell integration in your init scripts which will activate it even when launched outside VS Code. To test, read the updated documentation at https://github.com/microsoft/vscode-docs/blob/vnext/docs/terminal/shell-integration.md#manual-installation.
Some things to test in particular:
- Shell integration still works when manually installed _and_ automatic injection is enabled and working
- Manual install doesn't break other terminals (the if condition blocks that)
- Try inlining the script https://github.com/microsoft/vscode-docs/blob/vnext/docs/terminal/shell-integration.md#portability-vs-performance | 1.0 | Test: Shell integration manual install - Refs: #153921
- [x] macOS @tanhakabir
- [x] linux @deepak1556
- [x] windows @hediet
- [x] WSL @joyceerhl (or any remote)
Complexity: 3
Authors: @Tyriar, @meganrogge
Roles: Developer, Engineering Manager
[Create Issue](https://github.com/microsoft/vscode/issues/new?body=Testing+%23156001%0A%0A&assignees=Tyriar,meganrogge)
---
Shell integration should be activated manually for the original shell launched in the terminal, but not in sub-shells. To workaround this you can manually install shell integration in your init scripts which will activate it even when launched outside VS Code. To test, read the updated documentation at https://github.com/microsoft/vscode-docs/blob/vnext/docs/terminal/shell-integration.md#manual-installation.
Some things to test in particular:
- Shell integration still works when manually installed _and_ automatic injection is enabled and working
- Manual install doesn't break other terminals (the if condition blocks that)
- Try inlining the script https://github.com/microsoft/vscode-docs/blob/vnext/docs/terminal/shell-integration.md#portability-vs-performance | non_defect | test shell integration manual install refs macos tanhakabir linux windows hediet wsl joyceerhl or any remote complexity authors tyriar meganrogge roles developer engineering manager shell integration should be activated manually for the original shell launched in the terminal but not in sub shells to workaround this you can manually install shell integration in your init scripts which will activate it even when launched outside vs code to test read the updated documentation at some things to test in particular shell integration still works when manually installed and automatic injection is enabled and working manual install doesn t break other terminals the if condition blocks that try inlining the script | 0 |
18,680 | 3,080,680,538 | IssuesEvent | 2015-08-22 00:32:15 | jameslh/pagedown | https://api.github.com/repos/jameslh/pagedown | closed | Backslash character escapes two following characters | auto-migrated Priority-Medium Type-Defect | ```
> c.makeHtml('\\.**foo**');
Actual: '<p>.*<em>foo</em>*</p>'
Expected: '<p>.<strong>foo</strong></p>'
> c.makeHtml('\\***foo**\\*');
Actual: '<p>**<em>foo</em>**</p>'
Expected: '<p>*<strong>foo</strong>*</p>'
> c.makeHtml('\\[*a*\\](b)');
Actual: '<p>[*a*](b)</p>'
Expected: '<p>[<em>a</em>](b)</p>'
Tested on c245b9e.
```
Original issue reported on code.google.com by `pkoszulinski` on 7 Apr 2013 at 7:30 | 1.0 | Backslash character escapes two following characters - ```
> c.makeHtml('\\.**foo**');
Actual: '<p>.*<em>foo</em>*</p>'
Expected: '<p>.<strong>foo</strong></p>'
> c.makeHtml('\\***foo**\\*');
Actual: '<p>**<em>foo</em>**</p>'
Expected: '<p>*<strong>foo</strong>*</p>'
> c.makeHtml('\\[*a*\\](b)');
Actual: '<p>[*a*](b)</p>'
Expected: '<p>[<em>a</em>](b)</p>'
Tested on c245b9e.
```
Original issue reported on code.google.com by `pkoszulinski` on 7 Apr 2013 at 7:30 | defect | backslash character escapes two following characters c makehtml foo actual foo expected foo c makehtml foo actual foo expected foo c makehtml b actual b expected b tested on original issue reported on code google com by pkoszulinski on apr at | 1 |
12,566 | 2,708,303,092 | IssuesEvent | 2015-04-08 07:56:52 | bridgedotnet/Bridge | https://api.github.com/repos/bridgedotnet/Bridge | opened | Bridge.NET's Array.get() throws exception when array outside of boundaries | defect | For C#, when an array is touched outside its allocated area, and exception is thrown, as it could be touching any unexpected memory address.
For JavaScript, this is not true. Accessing an array beyond its boundaries just returns 'null' if that's actually beyond arrays' defined data. Also returns null when the element has not been set (non-contiguous arrays).
PoC:
The C# code:
```
namespace ClassLibrary1
{
public partial class Class1
{
public static int[] MyArray = new int[5];
public static int[,] My2DArray = new int[5, 5];
[Ready]
public static void TriggerError()
{
Console.Log("Array value outside its bounds is: " + MyArray[10]);
Console.Log("Next command will trigger an exception, whereas it should just show 'null'.");
Console.Log("Breaking array outside its bounds is: " + My2DArray[2, 10]);
}
}
}
```
Will result in the JS code:
```
Bridge.define('ClassLibrary1.Class1', {
statics: {
config: {
init: function () {
this.myArray = new Array(5);
this.my2DArray = Bridge.Array.create(0, null, 5, 5);
Bridge.ready(this.triggerError);
}
},
triggerError: function () {
console.log("Array value outside its bounds is: " + ClassLibrary1.Class1.myArray[10]);
console.log("Next command will trigger an exception, whereas it should just show 'null'.");
console.log("Breaking array outside its bounds is: " + ClassLibrary1.Class1.my2DArray.get([2, 10]));
}
}
});
```
And an exception will be triggered once the third command on `triggerError` function is executed on the browser. The exception is thrown from Bridge.Array.get(), corresponding to:
```
Bridge.js:4275 if (indices[i] < 0 || indices[i] >= arr.$s[i]) {
Bridge.js:4276 throw new Bridge.ArgumentException("Index " + i + " out of range");
BRidge.js:4277 }
```
| 1.0 | Bridge.NET's Array.get() throws exception when array outside of boundaries - For C#, when an array is touched outside its allocated area, and exception is thrown, as it could be touching any unexpected memory address.
For JavaScript, this is not true. Accessing an array beyond its boundaries just returns 'null' if that's actually beyond arrays' defined data. Also returns null when the element has not been set (non-contiguous arrays).
PoC:
The C# code:
```
namespace ClassLibrary1
{
public partial class Class1
{
public static int[] MyArray = new int[5];
public static int[,] My2DArray = new int[5, 5];
[Ready]
public static void TriggerError()
{
Console.Log("Array value outside its bounds is: " + MyArray[10]);
Console.Log("Next command will trigger an exception, whereas it should just show 'null'.");
Console.Log("Breaking array outside its bounds is: " + My2DArray[2, 10]);
}
}
}
```
Will result in the JS code:
```
Bridge.define('ClassLibrary1.Class1', {
statics: {
config: {
init: function () {
this.myArray = new Array(5);
this.my2DArray = Bridge.Array.create(0, null, 5, 5);
Bridge.ready(this.triggerError);
}
},
triggerError: function () {
console.log("Array value outside its bounds is: " + ClassLibrary1.Class1.myArray[10]);
console.log("Next command will trigger an exception, whereas it should just show 'null'.");
console.log("Breaking array outside its bounds is: " + ClassLibrary1.Class1.my2DArray.get([2, 10]));
}
}
});
```
And an exception will be triggered once the third command on `triggerError` function is executed on the browser. The exception is thrown from Bridge.Array.get(), corresponding to:
```
Bridge.js:4275 if (indices[i] < 0 || indices[i] >= arr.$s[i]) {
Bridge.js:4276 throw new Bridge.ArgumentException("Index " + i + " out of range");
BRidge.js:4277 }
```
| defect | bridge net s array get throws exception when array outside of boundaries for c when an array is touched outside its allocated area and exception is thrown as it could be touching any unexpected memory address for javascript this is not true accessing an array beyond its boundaries just returns null if that s actually beyond arrays defined data also returns null when the element has not been set non contiguous arrays poc the c code namespace public partial class public static int myarray new int public static int new int public static void triggererror console log array value outside its bounds is myarray console log next command will trigger an exception whereas it should just show null console log breaking array outside its bounds is will result in the js code bridge define statics config init function this myarray new array this bridge array create null bridge ready this triggererror triggererror function console log array value outside its bounds is myarray console log next command will trigger an exception whereas it should just show null console log breaking array outside its bounds is get and an exception will be triggered once the third command on triggererror function is executed on the browser the exception is thrown from bridge array get corresponding to bridge js if indices arr s bridge js throw new bridge argumentexception index i out of range bridge js | 1 |
232,174 | 25,565,391,362 | IssuesEvent | 2022-11-30 13:57:48 | hygieia/hygieia-whitesource-collector | https://api.github.com/repos/hygieia/hygieia-whitesource-collector | closed | CVE-2020-35490 (High) detected in jackson-databind-2.8.11.3.jar - autoclosed | wontfix security vulnerability | ## CVE-2020-35490 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.11.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.11.3/jackson-databind-2.8.11.3.jar</p>
<p>
Dependency Hierarchy:
- core-3.15.42.jar (Root Library)
- spring-boot-starter-web-1.5.22.RELEASE.jar
- :x: **jackson-databind-2.8.11.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/hygieia/hygieia-whitesource-collector/commit/4b5ed1d2f3030d721692ff4f980e8d2467fde19b">4b5ed1d2f3030d721692ff4f980e8d2467fde19b</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.dbcp2.datasources.PerUserPoolDataSource.
<p>Publish Date: 2020-12-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-35490>CVE-2020-35490</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-12-17</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-35490 (High) detected in jackson-databind-2.8.11.3.jar - autoclosed - ## CVE-2020-35490 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.11.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.11.3/jackson-databind-2.8.11.3.jar</p>
<p>
Dependency Hierarchy:
- core-3.15.42.jar (Root Library)
- spring-boot-starter-web-1.5.22.RELEASE.jar
- :x: **jackson-databind-2.8.11.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/hygieia/hygieia-whitesource-collector/commit/4b5ed1d2f3030d721692ff4f980e8d2467fde19b">4b5ed1d2f3030d721692ff4f980e8d2467fde19b</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.dbcp2.datasources.PerUserPoolDataSource.
<p>Publish Date: 2020-12-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-35490>CVE-2020-35490</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-12-17</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_defect | cve high detected in jackson databind jar autoclosed cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy core jar root library spring boot starter web release jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache commons datasources peruserpooldatasource publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with mend | 0 |
48,052 | 12,140,371,639 | IssuesEvent | 2020-04-23 20:25:32 | tensorflow/tensorflow | https://api.github.com/repos/tensorflow/tensorflow | closed | libcuda.so.1 is missing with conda env tf-gpu | stat:awaiting response type:build/install | I get the following errors:
```
2020-04-19 05:56:24.050072: W tensorflow/stream_executor/platform/default/dso_loader.cc:55] Could not load dynamic library 'libcuda.so.1'; dlerror: libcuda.so.1: cannot open shared object file: No such file or directory
2020-04-19 05:56:24.050125: E tensorflow/stream_executor/cuda/cuda_driver.cc:351] failed call to cuInit: UNKNOWN ERROR (303)
2020-04-19 05:56:24.050149: I tensorflow/stream_executor/cuda/cuda_diagnostics.cc:163] no NVIDIA GPU device is present: /dev/nvidia0 does not exist
2020-04-19 05:56:24.050476: I tensorflow/core/platform/cpu_feature_guard.cc:142] Your CPU supports instructions that this TensorFlow binary was not compiled to use: SSE4.1 SSE4.2 AVX AVX2 FMA
2020-04-19 05:56:24.066026: I tensorflow/core/platform/profile_utils/cpu_utils.cc:94] CPU Frequency: 2199900000 Hz
2020-04-19 05:56:24.068548: I tensorflow/compiler/xla/service/service.cc:168] XLA service 0x558e75a5b2c0 initialized for platform Host (this does not guarantee that XLA will be used). Devices:
2020-04-19 05:56:24.068591: I tensorflow/compiler/xla/service/service.cc:176] StreamExecutor device (0): Host, Default Version
WARNING:root:Limited tf.compat.v2.summary API due to missing TensorBoard installation.
WARNING:root:Limited tf.compat.v2.summary API due to missing TensorBoard installation.
WARNING:root:Limited tf.compat.v2.summary API due to missing TensorBoard installation.
```
when I execute
```
trainds = tf.data.Dataset.from_tensor_slices((helper.trainx,helper.trainm,helper.trainy)).batch(setup['BatchSize'])
```
Tensorflow cannot find the file libcuda.so.1.
I get this error in a Docker Container which uses miniconda and the tensorflow-gpu environment.
```
FROM continuumio/miniconda3
RUN conda create -n tf-gpu tensorflow-gpu
```
I don't get the error on my local machine with the same code.
As far as I understood, conda should automatically install cuda and its libraries.
When I search for the missing file I get an empty line. `find -name "libcuda.so.1"`
Other versions of libcuda.so. can't be found either. Even `*cuda*` couldn't be found. It seems to be that cuda was entirely skipped during the installation.
nvidia-smi returns this:
```
+-----------------------------------------------------------------------------+
| NVIDIA-SMI 410.104 Driver Version: 410.104 CUDA Version: N/A |
|-------------------------------+----------------------+----------------------+
| GPU Name Persistence-M| Bus-Id Disp.A | Volatile Uncorr. ECC |
| Fan Temp Perf Pwr:Usage/Cap| Memory-Usage | GPU-Util Compute M. |
|===============================+======================+======================|
| 0 Tesla P100-SXM2... Off | 00000000:89:00.0 Off | 0 |
| N/A 30C P0 31W / 300W | 0MiB / 16280MiB | 0% Default |
+-------------------------------+----------------------+----------------------+
+-----------------------------------------------------------------------------+
| Processes: GPU Memory |
| GPU PID Type Process name Usage |
|=============================================================================|
| No running processes found |
+-----------------------------------------------------------------------------+
```
**System information**
```
Python 3.7.6 | packaged by conda-forge | (default, Mar 23 2020, 23:03:20)
[GCC 7.3.0] on linux
```
- TensorFlow version: 2.1.0
- Python version: 3.7.6
- GPU model and memory: P100 / 16 GB
Additional information:
```
print(tf.test.is_gpu_available()) # False
print(tf.config.list_physical_devices('GPU')) # []
```
| 1.0 | libcuda.so.1 is missing with conda env tf-gpu - I get the following errors:
```
2020-04-19 05:56:24.050072: W tensorflow/stream_executor/platform/default/dso_loader.cc:55] Could not load dynamic library 'libcuda.so.1'; dlerror: libcuda.so.1: cannot open shared object file: No such file or directory
2020-04-19 05:56:24.050125: E tensorflow/stream_executor/cuda/cuda_driver.cc:351] failed call to cuInit: UNKNOWN ERROR (303)
2020-04-19 05:56:24.050149: I tensorflow/stream_executor/cuda/cuda_diagnostics.cc:163] no NVIDIA GPU device is present: /dev/nvidia0 does not exist
2020-04-19 05:56:24.050476: I tensorflow/core/platform/cpu_feature_guard.cc:142] Your CPU supports instructions that this TensorFlow binary was not compiled to use: SSE4.1 SSE4.2 AVX AVX2 FMA
2020-04-19 05:56:24.066026: I tensorflow/core/platform/profile_utils/cpu_utils.cc:94] CPU Frequency: 2199900000 Hz
2020-04-19 05:56:24.068548: I tensorflow/compiler/xla/service/service.cc:168] XLA service 0x558e75a5b2c0 initialized for platform Host (this does not guarantee that XLA will be used). Devices:
2020-04-19 05:56:24.068591: I tensorflow/compiler/xla/service/service.cc:176] StreamExecutor device (0): Host, Default Version
WARNING:root:Limited tf.compat.v2.summary API due to missing TensorBoard installation.
WARNING:root:Limited tf.compat.v2.summary API due to missing TensorBoard installation.
WARNING:root:Limited tf.compat.v2.summary API due to missing TensorBoard installation.
```
when I execute
```
trainds = tf.data.Dataset.from_tensor_slices((helper.trainx,helper.trainm,helper.trainy)).batch(setup['BatchSize'])
```
Tensorflow cannot find the file libcuda.so.1.
I get this error in a Docker Container which uses miniconda and the tensorflow-gpu environment.
```
FROM continuumio/miniconda3
RUN conda create -n tf-gpu tensorflow-gpu
```
I don't get the error on my local machine with the same code.
As far as I understood, conda should automatically install cuda and its libraries.
When I search for the missing file I get an empty line. `find -name "libcuda.so.1"`
Other versions of libcuda.so. can't be found either. Even `*cuda*` couldn't be found. It seems to be that cuda was entirely skipped during the installation.
nvidia-smi returns this:
```
+-----------------------------------------------------------------------------+
| NVIDIA-SMI 410.104 Driver Version: 410.104 CUDA Version: N/A |
|-------------------------------+----------------------+----------------------+
| GPU Name Persistence-M| Bus-Id Disp.A | Volatile Uncorr. ECC |
| Fan Temp Perf Pwr:Usage/Cap| Memory-Usage | GPU-Util Compute M. |
|===============================+======================+======================|
| 0 Tesla P100-SXM2... Off | 00000000:89:00.0 Off | 0 |
| N/A 30C P0 31W / 300W | 0MiB / 16280MiB | 0% Default |
+-------------------------------+----------------------+----------------------+
+-----------------------------------------------------------------------------+
| Processes: GPU Memory |
| GPU PID Type Process name Usage |
|=============================================================================|
| No running processes found |
+-----------------------------------------------------------------------------+
```
**System information**
```
Python 3.7.6 | packaged by conda-forge | (default, Mar 23 2020, 23:03:20)
[GCC 7.3.0] on linux
```
- TensorFlow version: 2.1.0
- Python version: 3.7.6
- GPU model and memory: P100 / 16 GB
Additional information:
```
print(tf.test.is_gpu_available()) # False
print(tf.config.list_physical_devices('GPU')) # []
```
| non_defect | libcuda so is missing with conda env tf gpu i get the following errors w tensorflow stream executor platform default dso loader cc could not load dynamic library libcuda so dlerror libcuda so cannot open shared object file no such file or directory e tensorflow stream executor cuda cuda driver cc failed call to cuinit unknown error i tensorflow stream executor cuda cuda diagnostics cc no nvidia gpu device is present dev does not exist i tensorflow core platform cpu feature guard cc your cpu supports instructions that this tensorflow binary was not compiled to use avx fma i tensorflow core platform profile utils cpu utils cc cpu frequency hz i tensorflow compiler xla service service cc xla service initialized for platform host this does not guarantee that xla will be used devices i tensorflow compiler xla service service cc streamexecutor device host default version warning root limited tf compat summary api due to missing tensorboard installation warning root limited tf compat summary api due to missing tensorboard installation warning root limited tf compat summary api due to missing tensorboard installation when i execute trainds tf data dataset from tensor slices helper trainx helper trainm helper trainy batch setup tensorflow cannot find the file libcuda so i get this error in a docker container which uses miniconda and the tensorflow gpu environment from continuumio run conda create n tf gpu tensorflow gpu i don t get the error on my local machine with the same code as far as i understood conda should automatically install cuda and its libraries when i search for the missing file i get an empty line find name libcuda so other versions of libcuda so can t be found either even cuda couldn t be found it seems to be that cuda was entirely skipped during the installation nvidia smi returns this nvidia smi driver version cuda version n a gpu name persistence m bus id disp a volatile uncorr ecc fan temp perf pwr usage cap memory usage gpu util compute m tesla off off n a default processes gpu memory gpu pid type process name usage no running processes found system information python packaged by conda forge default mar on linux tensorflow version python version gpu model and memory gb additional information print tf test is gpu available false print tf config list physical devices gpu | 0 |
81,665 | 31,237,988,856 | IssuesEvent | 2023-08-20 14:08:08 | cython/cython | https://api.github.com/repos/cython/cython | closed | [BUG] Compiler crashes when one enum class references another | defect | ### Describe the bug
I have two enum classes where one of them references members of the other. The Cython compiler crashes when parsing the second enum class definition at the point of the reference to the first, specifically when attempting to access a member.
### Code to reproduce the behavior:
```cython
# distutils: language = c++
from libcpp cimport bool as cbool
from libc.stdint cimport int8_t # Could also use something simpler like int, which I tried.
cdef enum class Color(int8_t):
RED = 1
GREEN = 2
cdef enum class Color2(int8_t):
RED = (<int8_t> Color.RED)
GREEN = (<int8_t> Color.GREEN)
```
This results in:
```
(test_cython_3) vyasr-dt% cythonize -i example2.pyx
Compiling /home/vyasr/local/testing/cython_cdef_enum/example2.pyx because it changed.
[1/1] Cythonizing ...
Error compiling Cython file:
------------------------------------------------------------
...
RED = 1
GREEN = 2
cdef enum class Color2(int8_t):
RED = (<int8_t> Color.RED)
^
------------------------------------------------------------
example2.pyx:13:25: Compiler crash in AnalyseDeclarationsTransform
File 'ModuleNode.py', line 203, in analyse_declarations: ModuleNode(example2.pyx:1:0,
full_module_name = 'example2')
File 'Nodes.py', line 393, in analyse_declarations: StatListNode(example2.pyx:3:0)
File 'Nodes.py', line 1728, in analyse_declarations: CEnumDefNode(example2.pyx:12:5,
name = 'Color2',
scoped = True,
visibility = 'private')
File 'Nodes.py', line 1766, in analyse_enum_declarations: CEnumDefItemNode(example2.pyx:13:4,
name = 'RED')
File 'ExprNodes.py', line 628, in analyse_const_expression: TypecastNode(example2.pyx:13:11,
result_is_used = True,
use_managed_ref = True)
File 'ExprNodes.py', line 10936, in analyse_types: TypecastNode(example2.pyx:13:11,
result_is_used = True,
use_managed_ref = True)
File 'ExprNodes.py', line 7323, in analyse_types: AttributeNode(example2.pyx:13:25,
attribute = 'RED',
is_attribute = 1,
needs_none_check = True,
result_is_used = True,
use_managed_ref = True)
Compiler crash traceback from this point on:
File "/home/vyasr/miniconda3/envs/test_cython_3/lib/python3.10/site-packages/Cython/Compiler/ExprNodes.py", line 7323, in analyse_types
self.initialized_check = env.directives['initializedcheck']
AttributeError: 'CppScopedEnumScope' object has no attribute 'directives'
Traceback (most recent call last):
File "/home/vyasr/miniconda3/envs/test_cython_3/bin/cythonize", line 11, in <module>
sys.exit(main())
File "/home/vyasr/miniconda3/envs/test_cython_3/lib/python3.10/site-packages/Cython/Build/Cythonize.py", line 243, in main
_cython_compile_files(all_paths, options)
File "/home/vyasr/miniconda3/envs/test_cython_3/lib/python3.10/site-packages/Cython/Build/Cythonize.py", line 70, in _cython_compile_files
ext_modules = cythonize(
File "/home/vyasr/miniconda3/envs/test_cython_3/lib/python3.10/site-packages/Cython/Build/Dependencies.py", line 1134, in cythonize
cythonize_one(*args)
File "/home/vyasr/miniconda3/envs/test_cython_3/lib/python3.10/site-packages/Cython/Build/Dependencies.py", line 1301, in cythonize_one
raise CompileError(None, pyx_file)
Cython.Compiler.Errors.CompileError: /home/vyasr/local/testing/cython_cdef_enum/example2.pyx
```
### Expected behaviour
This should compile successfully.
### OS
Linux
### Python version
3.10.2
### Cython version
3.0.0
### Additional context
This particular example is of course a contrived MWE. The practical use case I had in mind is wrapping a `cdef extern` `cdef enum class` corresponding to a C++ enum into a `cpdef enum class` that may be used by Python and Cython consumers of a Cython module. I have made sure that the two enums have the same underlying integral types, and I've included the appropriate casts. The equivalent C++ code (which compiles fine) would be something like:
```
enum class Color : int {
RED,
GREEN
};
enum class Color2 : int {
RED = static_cast<int>(Color::RED),
GREEN = static_cast<int>(Color::GREEN)
};
int main() {
auto x = Color2::RED;
}
``` | 1.0 | [BUG] Compiler crashes when one enum class references another - ### Describe the bug
I have two enum classes where one of them references members of the other. The Cython compiler crashes when parsing the second enum class definition at the point of the reference to the first, specifically when attempting to access a member.
### Code to reproduce the behavior:
```cython
# distutils: language = c++
from libcpp cimport bool as cbool
from libc.stdint cimport int8_t # Could also use something simpler like int, which I tried.
cdef enum class Color(int8_t):
RED = 1
GREEN = 2
cdef enum class Color2(int8_t):
RED = (<int8_t> Color.RED)
GREEN = (<int8_t> Color.GREEN)
```
This results in:
```
(test_cython_3) vyasr-dt% cythonize -i example2.pyx
Compiling /home/vyasr/local/testing/cython_cdef_enum/example2.pyx because it changed.
[1/1] Cythonizing ...
Error compiling Cython file:
------------------------------------------------------------
...
RED = 1
GREEN = 2
cdef enum class Color2(int8_t):
RED = (<int8_t> Color.RED)
^
------------------------------------------------------------
example2.pyx:13:25: Compiler crash in AnalyseDeclarationsTransform
File 'ModuleNode.py', line 203, in analyse_declarations: ModuleNode(example2.pyx:1:0,
full_module_name = 'example2')
File 'Nodes.py', line 393, in analyse_declarations: StatListNode(example2.pyx:3:0)
File 'Nodes.py', line 1728, in analyse_declarations: CEnumDefNode(example2.pyx:12:5,
name = 'Color2',
scoped = True,
visibility = 'private')
File 'Nodes.py', line 1766, in analyse_enum_declarations: CEnumDefItemNode(example2.pyx:13:4,
name = 'RED')
File 'ExprNodes.py', line 628, in analyse_const_expression: TypecastNode(example2.pyx:13:11,
result_is_used = True,
use_managed_ref = True)
File 'ExprNodes.py', line 10936, in analyse_types: TypecastNode(example2.pyx:13:11,
result_is_used = True,
use_managed_ref = True)
File 'ExprNodes.py', line 7323, in analyse_types: AttributeNode(example2.pyx:13:25,
attribute = 'RED',
is_attribute = 1,
needs_none_check = True,
result_is_used = True,
use_managed_ref = True)
Compiler crash traceback from this point on:
File "/home/vyasr/miniconda3/envs/test_cython_3/lib/python3.10/site-packages/Cython/Compiler/ExprNodes.py", line 7323, in analyse_types
self.initialized_check = env.directives['initializedcheck']
AttributeError: 'CppScopedEnumScope' object has no attribute 'directives'
Traceback (most recent call last):
File "/home/vyasr/miniconda3/envs/test_cython_3/bin/cythonize", line 11, in <module>
sys.exit(main())
File "/home/vyasr/miniconda3/envs/test_cython_3/lib/python3.10/site-packages/Cython/Build/Cythonize.py", line 243, in main
_cython_compile_files(all_paths, options)
File "/home/vyasr/miniconda3/envs/test_cython_3/lib/python3.10/site-packages/Cython/Build/Cythonize.py", line 70, in _cython_compile_files
ext_modules = cythonize(
File "/home/vyasr/miniconda3/envs/test_cython_3/lib/python3.10/site-packages/Cython/Build/Dependencies.py", line 1134, in cythonize
cythonize_one(*args)
File "/home/vyasr/miniconda3/envs/test_cython_3/lib/python3.10/site-packages/Cython/Build/Dependencies.py", line 1301, in cythonize_one
raise CompileError(None, pyx_file)
Cython.Compiler.Errors.CompileError: /home/vyasr/local/testing/cython_cdef_enum/example2.pyx
```
### Expected behaviour
This should compile successfully.
### OS
Linux
### Python version
3.10.2
### Cython version
3.0.0
### Additional context
This particular example is of course a contrived MWE. The practical use case I had in mind is wrapping a `cdef extern` `cdef enum class` corresponding to a C++ enum into a `cpdef enum class` that may be used by Python and Cython consumers of a Cython module. I have made sure that the two enums have the same underlying integral types, and I've included the appropriate casts. The equivalent C++ code (which compiles fine) would be something like:
```
enum class Color : int {
RED,
GREEN
};
enum class Color2 : int {
RED = static_cast<int>(Color::RED),
GREEN = static_cast<int>(Color::GREEN)
};
int main() {
auto x = Color2::RED;
}
``` | defect | compiler crashes when one enum class references another describe the bug i have two enum classes where one of them references members of the other the cython compiler crashes when parsing the second enum class definition at the point of the reference to the first specifically when attempting to access a member code to reproduce the behavior cython distutils language c from libcpp cimport bool as cbool from libc stdint cimport t could also use something simpler like int which i tried cdef enum class color t red green cdef enum class t red color red green color green this results in test cython vyasr dt cythonize i pyx compiling home vyasr local testing cython cdef enum pyx because it changed cythonizing error compiling cython file red green cdef enum class t red color red pyx compiler crash in analysedeclarationstransform file modulenode py line in analyse declarations modulenode pyx full module name file nodes py line in analyse declarations statlistnode pyx file nodes py line in analyse declarations cenumdefnode pyx name scoped true visibility private file nodes py line in analyse enum declarations cenumdefitemnode pyx name red file exprnodes py line in analyse const expression typecastnode pyx result is used true use managed ref true file exprnodes py line in analyse types typecastnode pyx result is used true use managed ref true file exprnodes py line in analyse types attributenode pyx attribute red is attribute needs none check true result is used true use managed ref true compiler crash traceback from this point on file home vyasr envs test cython lib site packages cython compiler exprnodes py line in analyse types self initialized check env directives attributeerror cppscopedenumscope object has no attribute directives traceback most recent call last file home vyasr envs test cython bin cythonize line in sys exit main file home vyasr envs test cython lib site packages cython build cythonize py line in main cython compile files all paths options file home vyasr envs test cython lib site packages cython build cythonize py line in cython compile files ext modules cythonize file home vyasr envs test cython lib site packages cython build dependencies py line in cythonize cythonize one args file home vyasr envs test cython lib site packages cython build dependencies py line in cythonize one raise compileerror none pyx file cython compiler errors compileerror home vyasr local testing cython cdef enum pyx expected behaviour this should compile successfully os linux python version cython version additional context this particular example is of course a contrived mwe the practical use case i had in mind is wrapping a cdef extern cdef enum class corresponding to a c enum into a cpdef enum class that may be used by python and cython consumers of a cython module i have made sure that the two enums have the same underlying integral types and i ve included the appropriate casts the equivalent c code which compiles fine would be something like enum class color int red green enum class int red static cast color red green static cast color green int main auto x red | 1 |
43,435 | 11,716,152,795 | IssuesEvent | 2020-03-09 15:13:15 | primefaces/primefaces | https://api.github.com/repos/primefaces/primefaces | closed | Bean Validation: messages not show all labels | defect | Hi.
You can check it on primefaces showcase for bean validation.
https://www.primefaces.org/showcase/ui/csv/bean.xhtml
When messages component show validation error there few labels skipped (probably connected with some of annotations).
Labels which are skipped:
> Name
> Pattern
> Assert
> Radio input

| 1.0 | Bean Validation: messages not show all labels - Hi.
You can check it on primefaces showcase for bean validation.
https://www.primefaces.org/showcase/ui/csv/bean.xhtml
When messages component show validation error there few labels skipped (probably connected with some of annotations).
Labels which are skipped:
> Name
> Pattern
> Assert
> Radio input

| defect | bean validation messages not show all labels hi you can check it on primefaces showcase for bean validation when messages component show validation error there few labels skipped probably connected with some of annotations labels which are skipped name pattern assert radio input | 1 |
284,206 | 30,913,603,647 | IssuesEvent | 2023-08-05 02:22:14 | Satheesh575555/linux-4.1.15_CVE-2022-45934 | https://api.github.com/repos/Satheesh575555/linux-4.1.15_CVE-2022-45934 | reopened | CVE-2019-19047 (Medium) detected in linuxlinux-4.6 | Mend: dependency security vulnerability | ## CVE-2019-19047 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Satheesh575555/linux-4.1.15_CVE-2022-45934/commit/7c0b143b43394df131d83e9aecb3c5518edc127a">7c0b143b43394df131d83e9aecb3c5518edc127a</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/ethernet/mellanox/mlx5/core/health.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/ethernet/mellanox/mlx5/core/health.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
A memory leak in the mlx5_fw_fatal_reporter_dump() function in drivers/net/ethernet/mellanox/mlx5/core/health.c in the Linux kernel before 5.3.11 allows attackers to cause a denial of service (memory consumption) by triggering mlx5_crdump_collect() failures, aka CID-c7ed6d0183d5.
<p>Publish Date: 2019-11-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-19047>CVE-2019-19047</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19047">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19047</a></p>
<p>Release Date: 2019-11-18</p>
<p>Fix Resolution: v5.4-rc6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-19047 (Medium) detected in linuxlinux-4.6 - ## CVE-2019-19047 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Satheesh575555/linux-4.1.15_CVE-2022-45934/commit/7c0b143b43394df131d83e9aecb3c5518edc127a">7c0b143b43394df131d83e9aecb3c5518edc127a</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/ethernet/mellanox/mlx5/core/health.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/ethernet/mellanox/mlx5/core/health.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
A memory leak in the mlx5_fw_fatal_reporter_dump() function in drivers/net/ethernet/mellanox/mlx5/core/health.c in the Linux kernel before 5.3.11 allows attackers to cause a denial of service (memory consumption) by triggering mlx5_crdump_collect() failures, aka CID-c7ed6d0183d5.
<p>Publish Date: 2019-11-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-19047>CVE-2019-19047</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19047">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19047</a></p>
<p>Release Date: 2019-11-18</p>
<p>Fix Resolution: v5.4-rc6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_defect | cve medium detected in linuxlinux cve medium severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch master vulnerable source files drivers net ethernet mellanox core health c drivers net ethernet mellanox core health c vulnerability details a memory leak in the fw fatal reporter dump function in drivers net ethernet mellanox core health c in the linux kernel before allows attackers to cause a denial of service memory consumption by triggering crdump collect failures aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
34,310 | 7,440,737,975 | IssuesEvent | 2018-03-27 11:07:23 | primefaces/primeng | https://api.github.com/repos/primefaces/primeng | closed | InputTextarea does not resize initial value | defect | **I'm submitting a ...** (check one with "x")
```
[x] bug report => Search github for a similar issue or PR before submitting
[ ] feature request => Please check if request is not on the roadmap already https://github.com/primefaces/primeng/wiki/Roadmap
[ ] support request => Please do not submit support request here, instead see http://forum.primefaces.org/viewforum.php?f=35
```
**Plunkr Case (Bug Reports)**
http://plnkr.co/edit/8bQOjvCYpjgMhTNgPTFD?p=preview
**Current behavior**
I don´t know if it would better two reports, but I´ll explain them here
- First issue, when first load, the textinputarea dont resize until clicked. As a workaround I have call the resize method on init
- Second issue, the height is calculated on the cols and character number, no on the width. That means that the height will be too long, or too short, depending on the current cols value. A different approach would be to calculate the height based on the width
* **PrimeNG version:** 5.0.2
* **Browser:** Chrome
| 1.0 | InputTextarea does not resize initial value - **I'm submitting a ...** (check one with "x")
```
[x] bug report => Search github for a similar issue or PR before submitting
[ ] feature request => Please check if request is not on the roadmap already https://github.com/primefaces/primeng/wiki/Roadmap
[ ] support request => Please do not submit support request here, instead see http://forum.primefaces.org/viewforum.php?f=35
```
**Plunkr Case (Bug Reports)**
http://plnkr.co/edit/8bQOjvCYpjgMhTNgPTFD?p=preview
**Current behavior**
I don´t know if it would better two reports, but I´ll explain them here
- First issue, when first load, the textinputarea dont resize until clicked. As a workaround I have call the resize method on init
- Second issue, the height is calculated on the cols and character number, no on the width. That means that the height will be too long, or too short, depending on the current cols value. A different approach would be to calculate the height based on the width
* **PrimeNG version:** 5.0.2
* **Browser:** Chrome
| defect | inputtextarea does not resize initial value i m submitting a check one with x bug report search github for a similar issue or pr before submitting feature request please check if request is not on the roadmap already support request please do not submit support request here instead see plunkr case bug reports current behavior i don´t know if it would better two reports but i´ll explain them here first issue when first load the textinputarea dont resize until clicked as a workaround i have call the resize method on init second issue the height is calculated on the cols and character number no on the width that means that the height will be too long or too short depending on the current cols value a different approach would be to calculate the height based on the width primeng version browser chrome | 1 |
73,339 | 24,574,655,241 | IssuesEvent | 2022-10-13 11:22:11 | jOOQ/jOOQ | https://api.github.com/repos/jOOQ/jOOQ | closed | DDLDatabase defaultNameCase broken for enum columns | T: Defect C: Functionality P: Medium E: All Editions | ### Expected behavior
In the schema below, DDLDatabase should apply `defaultNameCase` to enum types just as it does for table or column names.
```
create type fruit as enum ( 'APPLE', 'PEAR', 'ORANGE' );
create table if not exists test_table
(
fruits fruit[] not null
);
```
### Actual behavior
While the enum type is created with the correct name (quoted & lowercased), its reference in the table definition is transformed to uppercase and thus not recognized:
```
[INFO] create type "fruit" as enum ('APPLE', 'PEAR', 'ORANGE')
[INFO] Update count: 0
[INFO] create table if not exists "test_table" (
"fruits" FRUIT array not null
)
[ERROR] DDLDatabase Error : Your SQL string could not be parsed or interpreted.
```
I tried switching the table column type from `fruit[]` to `"fruit"[]` so that it matches the transformed `create type` command, but that is transformed into an unquoted lowercase type name which doesn't work either:
```
[INFO] create type "fruit" as enum ('APPLE', 'PEAR', 'ORANGE')
[INFO] Update count: 0
[INFO] create table if not exists "test_table" (
"fruits" fruit array not null
)
[ERROR] DDLDatabase Error : Your SQL string could not be parsed or interpreted.
```
### Steps to reproduce the problem
Use the following code generator settings:
```
<plugin>
<groupId>org.jooq</groupId>
<artifactId>jooq-codegen-maven</artifactId>
<version>${org.jooq.version}</version>
<dependencies>
<dependency>
<groupId>org.jooq</groupId>
<artifactId>jooq-meta-extensions</artifactId>
<version>${org.jooq.version}</version>
</dependency>
</dependencies>
<executions>
<execution>
<id>jooq-codegen</id>
<goals>
<goal>generate</goal>
</goals>
<phase>generate-sources</phase>
<configuration>
<generator>
<database>
<name>org.jooq.meta.extensions.ddl.DDLDatabase</name>
<properties>
<property>
<key>scripts</key>
<value>${project.basedir}/src/main/db/schema.sql</value>
</property>
<property>
<key>defaultNameCase</key>
<value>lower</value>
</property>
<property>
<key>logExecutedQueries</key>
<value>true</value>
</property>
</properties>
</database>
</generator>
</configuration>
</execution>
</executions>
</plugin>
```
I also prepared an MCVE.
### Versions
- jOOQ: 3.16.3
- Java: 11.0.13_8
- Database: none for code generation (PostgreSQL 12 at runtime)
- OS: Windows
- JDBC Driver: none for code generation (org.postgresql:postgresql:42.2.16 at runtime)
| 1.0 | DDLDatabase defaultNameCase broken for enum columns - ### Expected behavior
In the schema below, DDLDatabase should apply `defaultNameCase` to enum types just as it does for table or column names.
```
create type fruit as enum ( 'APPLE', 'PEAR', 'ORANGE' );
create table if not exists test_table
(
fruits fruit[] not null
);
```
### Actual behavior
While the enum type is created with the correct name (quoted & lowercased), its reference in the table definition is transformed to uppercase and thus not recognized:
```
[INFO] create type "fruit" as enum ('APPLE', 'PEAR', 'ORANGE')
[INFO] Update count: 0
[INFO] create table if not exists "test_table" (
"fruits" FRUIT array not null
)
[ERROR] DDLDatabase Error : Your SQL string could not be parsed or interpreted.
```
I tried switching the table column type from `fruit[]` to `"fruit"[]` so that it matches the transformed `create type` command, but that is transformed into an unquoted lowercase type name which doesn't work either:
```
[INFO] create type "fruit" as enum ('APPLE', 'PEAR', 'ORANGE')
[INFO] Update count: 0
[INFO] create table if not exists "test_table" (
"fruits" fruit array not null
)
[ERROR] DDLDatabase Error : Your SQL string could not be parsed or interpreted.
```
### Steps to reproduce the problem
Use the following code generator settings:
```
<plugin>
<groupId>org.jooq</groupId>
<artifactId>jooq-codegen-maven</artifactId>
<version>${org.jooq.version}</version>
<dependencies>
<dependency>
<groupId>org.jooq</groupId>
<artifactId>jooq-meta-extensions</artifactId>
<version>${org.jooq.version}</version>
</dependency>
</dependencies>
<executions>
<execution>
<id>jooq-codegen</id>
<goals>
<goal>generate</goal>
</goals>
<phase>generate-sources</phase>
<configuration>
<generator>
<database>
<name>org.jooq.meta.extensions.ddl.DDLDatabase</name>
<properties>
<property>
<key>scripts</key>
<value>${project.basedir}/src/main/db/schema.sql</value>
</property>
<property>
<key>defaultNameCase</key>
<value>lower</value>
</property>
<property>
<key>logExecutedQueries</key>
<value>true</value>
</property>
</properties>
</database>
</generator>
</configuration>
</execution>
</executions>
</plugin>
```
I also prepared an MCVE.
### Versions
- jOOQ: 3.16.3
- Java: 11.0.13_8
- Database: none for code generation (PostgreSQL 12 at runtime)
- OS: Windows
- JDBC Driver: none for code generation (org.postgresql:postgresql:42.2.16 at runtime)
| defect | ddldatabase defaultnamecase broken for enum columns expected behavior in the schema below ddldatabase should apply defaultnamecase to enum types just as it does for table or column names create type fruit as enum apple pear orange create table if not exists test table fruits fruit not null actual behavior while the enum type is created with the correct name quoted lowercased its reference in the table definition is transformed to uppercase and thus not recognized create type fruit as enum apple pear orange update count create table if not exists test table fruits fruit array not null ddldatabase error your sql string could not be parsed or interpreted i tried switching the table column type from fruit to fruit so that it matches the transformed create type command but that is transformed into an unquoted lowercase type name which doesn t work either create type fruit as enum apple pear orange update count create table if not exists test table fruits fruit array not null ddldatabase error your sql string could not be parsed or interpreted steps to reproduce the problem use the following code generator settings org jooq jooq codegen maven org jooq version org jooq jooq meta extensions org jooq version jooq codegen generate generate sources org jooq meta extensions ddl ddldatabase scripts project basedir src main db schema sql defaultnamecase lower logexecutedqueries true i also prepared an mcve versions jooq java database none for code generation postgresql at runtime os windows jdbc driver none for code generation org postgresql postgresql at runtime | 1 |
14,902 | 2,831,390,296 | IssuesEvent | 2015-05-24 15:55:09 | nobodyguy/dslrdashboard | https://api.github.com/repos/nobodyguy/dslrdashboard | closed | D7000 & LV Focus | auto-migrated Priority-Medium Type-Defect | ```
What steps will reproduce the problem?
1. LV Focus Selection
What is the expected output? What do you see instead?
Expected: Picture in Focus
Instead: Picture out of Focus
What version of the product are you using? On what operating system?
0.30.15 Android 4.2.1 on Nexus 7
Please provide any additional information below.
When using the Live View Touch Focus on my d7000 the focus is shown correctly
but when taking a picture, it appeared that the focus changed and the picture
is out of focus without changing the stationary object which was focused on.
```
Original issue reported on code.google.com by `thisisca...@gmail.com` on 24 Jan 2013 at 5:46 | 1.0 | D7000 & LV Focus - ```
What steps will reproduce the problem?
1. LV Focus Selection
What is the expected output? What do you see instead?
Expected: Picture in Focus
Instead: Picture out of Focus
What version of the product are you using? On what operating system?
0.30.15 Android 4.2.1 on Nexus 7
Please provide any additional information below.
When using the Live View Touch Focus on my d7000 the focus is shown correctly
but when taking a picture, it appeared that the focus changed and the picture
is out of focus without changing the stationary object which was focused on.
```
Original issue reported on code.google.com by `thisisca...@gmail.com` on 24 Jan 2013 at 5:46 | defect | lv focus what steps will reproduce the problem lv focus selection what is the expected output what do you see instead expected picture in focus instead picture out of focus what version of the product are you using on what operating system android on nexus please provide any additional information below when using the live view touch focus on my the focus is shown correctly but when taking a picture it appeared that the focus changed and the picture is out of focus without changing the stationary object which was focused on original issue reported on code google com by thisisca gmail com on jan at | 1 |
52,984 | 13,259,017,893 | IssuesEvent | 2020-08-20 16:08:24 | hikaya-io/activity | https://api.github.com/repos/hikaya-io/activity | closed | Indicator Results: Edit/Delete icons are not aligned | 1 defect good first issue | **Current behavior**
When you add multiple result entries under the same indicator, the `edit` and `delete` icons are mis-aligned
**To Reproduce**
Steps to reproduce the behavior:
1. Go to: Indicator
2. Click arrow to expand Indicator Results
3. See error
**Expected behavior**
The icons should right-aligned, similar to the first indicator result entered
**Screenshots**

| 1.0 | Indicator Results: Edit/Delete icons are not aligned - **Current behavior**
When you add multiple result entries under the same indicator, the `edit` and `delete` icons are mis-aligned
**To Reproduce**
Steps to reproduce the behavior:
1. Go to: Indicator
2. Click arrow to expand Indicator Results
3. See error
**Expected behavior**
The icons should right-aligned, similar to the first indicator result entered
**Screenshots**

| defect | indicator results edit delete icons are not aligned current behavior when you add multiple result entries under the same indicator the edit and delete icons are mis aligned to reproduce steps to reproduce the behavior go to indicator click arrow to expand indicator results see error expected behavior the icons should right aligned similar to the first indicator result entered screenshots | 1 |
13,324 | 2,753,739,582 | IssuesEvent | 2015-04-25 00:50:59 | sma-bluetooth/sma-bluetooth | https://api.github.com/repos/sma-bluetooth/sma-bluetooth | closed | Loading past data | auto-migrated Priority-Medium Type-Defect | ```
I just set up SMA-Bluetooth. Loaded the data to MySQL - all good.
How can I load all of the data from MySQL to PVOutput.org (have about 6
months)?
```
Original issue reported on code.google.com by `fok...@gmail.com` on 13 Sep 2011 at 6:28 | 1.0 | Loading past data - ```
I just set up SMA-Bluetooth. Loaded the data to MySQL - all good.
How can I load all of the data from MySQL to PVOutput.org (have about 6
months)?
```
Original issue reported on code.google.com by `fok...@gmail.com` on 13 Sep 2011 at 6:28 | defect | loading past data i just set up sma bluetooth loaded the data to mysql all good how can i load all of the data from mysql to pvoutput org have about months original issue reported on code google com by fok gmail com on sep at | 1 |
76,514 | 26,473,057,377 | IssuesEvent | 2023-01-17 09:04:39 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | Notify new voice broadcast | T-Defect S-Minor A-Notifications O-Uncommon Z-Labs A-Broadcast | ### Steps to reproduce
Since https://github.com/vector-im/element-web/issues/24101 we ignore on purpose the audio chunks of a voice broadcast during the notifications management.
Because of that change, we don't have any notification on a new voice broadcast
### Outcome
#### What did you expect?
With default notification settings:
During the notifications handling, we should notify only the first voice chunk of a voice broadcast, and ignore the other events related to the voice broadcast chunks
#### What happened instead?
No notification
### Operating system
_No response_
### Browser information
_No response_
### URL for webapp
_No response_
### Application version
_No response_
### Homeserver
_No response_
### Will you send logs?
No | 1.0 | Notify new voice broadcast - ### Steps to reproduce
Since https://github.com/vector-im/element-web/issues/24101 we ignore on purpose the audio chunks of a voice broadcast during the notifications management.
Because of that change, we don't have any notification on a new voice broadcast
### Outcome
#### What did you expect?
With default notification settings:
During the notifications handling, we should notify only the first voice chunk of a voice broadcast, and ignore the other events related to the voice broadcast chunks
#### What happened instead?
No notification
### Operating system
_No response_
### Browser information
_No response_
### URL for webapp
_No response_
### Application version
_No response_
### Homeserver
_No response_
### Will you send logs?
No | defect | notify new voice broadcast steps to reproduce since we ignore on purpose the audio chunks of a voice broadcast during the notifications management because of that change we don t have any notification on a new voice broadcast outcome what did you expect with default notification settings during the notifications handling we should notify only the first voice chunk of a voice broadcast and ignore the other events related to the voice broadcast chunks what happened instead no notification operating system no response browser information no response url for webapp no response application version no response homeserver no response will you send logs no | 1 |
17,728 | 3,012,944,518 | IssuesEvent | 2015-07-29 04:29:02 | yawlfoundation/yawl | https://api.github.com/repos/yawlfoundation/yawl | closed | What happens if I close the browser when I am logged into the resource service as "admin". | auto-migrated Component-ResService Priority-Medium Type-Defect | ```
I connected to resource service as "admin" and, then, I closed my browser
without logging out. I am using "Mozilla Firefox 3.0.4".
The result is that I remain logged in and, consequently, I cannot log in as
any user anymore.
When I do that, the only way to recover from this issue is to stop and
start the engine again. I guess that closing without logging out is not
infrequent for a typical user. Does the resource Service consider "admin"
(or any other user) as disconnected after a while?
```
Original issue reported on code.google.com by `maxdele...@gmail.com` on 16 Dec 2008 at 7:29 | 1.0 | What happens if I close the browser when I am logged into the resource service as "admin". - ```
I connected to resource service as "admin" and, then, I closed my browser
without logging out. I am using "Mozilla Firefox 3.0.4".
The result is that I remain logged in and, consequently, I cannot log in as
any user anymore.
When I do that, the only way to recover from this issue is to stop and
start the engine again. I guess that closing without logging out is not
infrequent for a typical user. Does the resource Service consider "admin"
(or any other user) as disconnected after a while?
```
Original issue reported on code.google.com by `maxdele...@gmail.com` on 16 Dec 2008 at 7:29 | defect | what happens if i close the browser when i am logged into the resource service as admin i connected to resource service as admin and then i closed my browser without logging out i am using mozilla firefox the result is that i remain logged in and consequently i cannot log in as any user anymore when i do that the only way to recover from this issue is to stop and start the engine again i guess that closing without logging out is not infrequent for a typical user does the resource service consider admin or any other user as disconnected after a while original issue reported on code google com by maxdele gmail com on dec at | 1 |
195,052 | 22,283,499,702 | IssuesEvent | 2022-06-11 08:31:52 | classicvalues/classicvalues-website-update | https://api.github.com/repos/classicvalues/classicvalues-website-update | closed | firebase-admin-7.4.0.tgz: 13 vulnerabilities (highest severity is: 7.5) - autoclosed | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>firebase-admin-7.4.0.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-forge/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2020-26289](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26289) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | date-and-time-0.6.3.tgz | Transitive | 8.8.0 | ❌ |
| [CVE-2022-25878](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-25878) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | protobufjs-5.0.3.tgz | Transitive | 8.0.0 | ❌ |
| [CVE-2020-7768](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7768) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | grpc-js-0.3.6.tgz | Transitive | 8.0.0 | ❌ |
| [CVE-2022-24434](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24434) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | dicer-0.3.1.tgz | Transitive | N/A | ❌ |
| [CVE-2022-24772](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24772) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | multiple | Transitive | 10.0.2 | ❌ |
| [CVE-2020-8237](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8237) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | json-bigint-0.3.1.tgz | Transitive | 9.0.0 | ❌ |
| [CVE-2022-24771](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24771) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | multiple | Transitive | 10.0.2 | ❌ |
| [WS-2020-0219](https://github.com/knowledgecode/date-and-time/commit/9e4b501eacddccc8b1f559fb414f48472ee17c2a) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | date-and-time-0.6.3.tgz | Transitive | 8.8.0 | ❌ |
| [CVE-2020-7720](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7720) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | node-forge-0.7.4.tgz | Transitive | 9.2.0 | ❌ |
| [WS-2022-0008](https://github.com/digitalbazaar/forge/commit/51228083550dde97701ac8e06c629a5184117562) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.6 | multiple | Transitive | 10.0.2 | ❌ |
| [CVE-2022-0122](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0122) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | multiple | Transitive | 10.0.2 | ❌ |
| [CVE-2022-24773](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24773) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | multiple | Transitive | 10.0.2 | ❌ |
| [CVE-2020-7765](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7765) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | util-0.2.14.tgz | Transitive | 9.4.2 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-26289</summary>
### Vulnerable Library - <b>date-and-time-0.6.3.tgz</b></p>
<p>A Minimalist DateTime utility for Node.js and the browser</p>
<p>Library home page: <a href="https://registry.npmjs.org/date-and-time/-/date-and-time-0.6.3.tgz">https://registry.npmjs.org/date-and-time/-/date-and-time-0.6.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/date-and-time/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- storage-2.5.0.tgz
- :x: **date-and-time-0.6.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
date-and-time is an npm package for manipulating date and time. In date-and-time before version 0.14.2, there a regular expression involved in parsing which can be exploited to to cause a denial of service. This is fixed in version 0.14.2.
<p>Publish Date: 2020-12-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26289>CVE-2020-26289</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-26289">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-26289</a></p>
<p>Release Date: 2020-12-28</p>
<p>Fix Resolution (date-and-time): 0.14.2</p>
<p>Direct dependency fix Resolution (firebase-admin): 8.8.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-25878</summary>
### Vulnerable Library - <b>protobufjs-5.0.3.tgz</b></p>
<p>Protocol Buffers for JavaScript. Finally.</p>
<p>Library home page: <a href="https://registry.npmjs.org/protobufjs/-/protobufjs-5.0.3.tgz">https://registry.npmjs.org/protobufjs/-/protobufjs-5.0.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/protobufjs/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- firestore-1.3.0.tgz
- google-gax-0.25.6.tgz
- grpc-1.24.11.tgz
- :x: **protobufjs-5.0.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package protobufjs before 6.11.3 are vulnerable to Prototype Pollution which can allow an attacker to add/modify properties of the Object.prototype. This vulnerability can occur in multiple ways: 1. by providing untrusted user input to util.setProperty or to ReflectionObject.setParsedOption functions 2. by parsing/loading .proto files
<p>Publish Date: 2022-05-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-25878>CVE-2022-25878</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25878">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25878</a></p>
<p>Release Date: 2022-05-27</p>
<p>Fix Resolution (protobufjs): 6.11.3</p>
<p>Direct dependency fix Resolution (firebase-admin): 8.0.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7768</summary>
### Vulnerable Library - <b>grpc-js-0.3.6.tgz</b></p>
<p>gRPC Library for Node - pure JS implementation</p>
<p>Library home page: <a href="https://registry.npmjs.org/@grpc/grpc-js/-/grpc-js-0.3.6.tgz">https://registry.npmjs.org/@grpc/grpc-js/-/grpc-js-0.3.6.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/google-gax/node_modules/@grpc/grpc-js/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- firestore-1.3.0.tgz
- google-gax-0.25.6.tgz
- :x: **grpc-js-0.3.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package grpc before 1.24.4; the package @grpc/grpc-js before 1.1.8 are vulnerable to Prototype Pollution via loadPackageDefinition.
<p>Publish Date: 2020-11-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7768>CVE-2020-7768</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7768">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7768</a></p>
<p>Release Date: 2020-11-11</p>
<p>Fix Resolution (@grpc/grpc-js): 1.1.8</p>
<p>Direct dependency fix Resolution (firebase-admin): 8.0.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-24434</summary>
### Vulnerable Library - <b>dicer-0.3.1.tgz</b></p>
<p>A very fast streaming multipart parser for node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/dicer/-/dicer-0.3.1.tgz">https://registry.npmjs.org/dicer/-/dicer-0.3.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/dicer/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- :x: **dicer-0.3.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects all versions of package dicer. A malicious attacker can send a modified form to server, and crash the nodejs service. An attacker could sent the payload again and again so that the service continuously crashes.
<p>Publish Date: 2022-05-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24434>CVE-2022-24434</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2022-24434">https://nvd.nist.gov/vuln/detail/CVE-2022-24434</a></p>
<p>Release Date: 2022-05-20</p>
<p>Fix Resolution: no_fix</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-24772</summary>
### Vulnerable Libraries - <b>node-forge-0.10.0.tgz</b>, <b>node-forge-0.7.4.tgz</b></p>
<p>
### <b>node-forge-0.10.0.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/google-p12-pem/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- storage-2.5.0.tgz
- gcs-resumable-upload-1.1.0.tgz
- google-auth-library-3.1.2.tgz
- gtoken-2.3.3.tgz
- google-p12-pem-1.0.5.tgz
- :x: **node-forge-0.10.0.tgz** (Vulnerable Library)
### <b>node-forge-0.7.4.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- :x: **node-forge-0.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Forge (also called `node-forge`) is a native implementation of Transport Layer Security in JavaScript. Prior to version 1.3.0, RSA PKCS#1 v1.5 signature verification code does not check for tailing garbage bytes after decoding a `DigestInfo` ASN.1 structure. This can allow padding bytes to be removed and garbage data added to forge a signature when a low public exponent is being used. The issue has been addressed in `node-forge` version 1.3.0. There are currently no known workarounds.
<p>Publish Date: 2022-03-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24772>CVE-2022-24772</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24772">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24772</a></p>
<p>Release Date: 2022-03-18</p>
<p>Fix Resolution (node-forge): 1.3.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 10.0.2</p><p>Fix Resolution (node-forge): 1.3.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 10.0.2</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-8237</summary>
### Vulnerable Library - <b>json-bigint-0.3.1.tgz</b></p>
<p>JSON.parse with bigints support</p>
<p>Library home page: <a href="https://registry.npmjs.org/json-bigint/-/json-bigint-0.3.1.tgz">https://registry.npmjs.org/json-bigint/-/json-bigint-0.3.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/json-bigint/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- storage-2.5.0.tgz
- gcs-resumable-upload-1.1.0.tgz
- google-auth-library-3.1.2.tgz
- gcp-metadata-1.0.0.tgz
- :x: **json-bigint-0.3.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Prototype pollution in json-bigint npm package < 1.0.0 may lead to a denial-of-service (DoS) attack.
<p>Publish Date: 2020-09-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8237>CVE-2020-8237</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://hackerone.com/reports/916430">https://hackerone.com/reports/916430</a></p>
<p>Release Date: 2020-09-30</p>
<p>Fix Resolution (json-bigint): 1.0.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 9.0.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-24771</summary>
### Vulnerable Libraries - <b>node-forge-0.10.0.tgz</b>, <b>node-forge-0.7.4.tgz</b></p>
<p>
### <b>node-forge-0.10.0.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/google-p12-pem/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- storage-2.5.0.tgz
- gcs-resumable-upload-1.1.0.tgz
- google-auth-library-3.1.2.tgz
- gtoken-2.3.3.tgz
- google-p12-pem-1.0.5.tgz
- :x: **node-forge-0.10.0.tgz** (Vulnerable Library)
### <b>node-forge-0.7.4.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- :x: **node-forge-0.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Forge (also called `node-forge`) is a native implementation of Transport Layer Security in JavaScript. Prior to version 1.3.0, RSA PKCS#1 v1.5 signature verification code is lenient in checking the digest algorithm structure. This can allow a crafted structure that steals padding bytes and uses unchecked portion of the PKCS#1 encoded message to forge a signature when a low public exponent is being used. The issue has been addressed in `node-forge` version 1.3.0. There are currently no known workarounds.
<p>Publish Date: 2022-03-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24771>CVE-2022-24771</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24771">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24771</a></p>
<p>Release Date: 2022-03-18</p>
<p>Fix Resolution (node-forge): 1.3.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 10.0.2</p><p>Fix Resolution (node-forge): 1.3.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 10.0.2</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2020-0219</summary>
### Vulnerable Library - <b>date-and-time-0.6.3.tgz</b></p>
<p>A Minimalist DateTime utility for Node.js and the browser</p>
<p>Library home page: <a href="https://registry.npmjs.org/date-and-time/-/date-and-time-0.6.3.tgz">https://registry.npmjs.org/date-and-time/-/date-and-time-0.6.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/date-and-time/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- storage-2.5.0.tgz
- :x: **date-and-time-0.6.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Due to an overly permissive regular expression, the parsing of certain date strings may lead to a denial of service.
<p>Publish Date: 2020-12-25
<p>URL: <a href=https://github.com/knowledgecode/date-and-time/commit/9e4b501eacddccc8b1f559fb414f48472ee17c2a>WS-2020-0219</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/knowledgecode/date-and-time/releases/tag/v0.14.2">https://github.com/knowledgecode/date-and-time/releases/tag/v0.14.2</a></p>
<p>Release Date: 2020-12-25</p>
<p>Fix Resolution (date-and-time): 0.14.2</p>
<p>Direct dependency fix Resolution (firebase-admin): 8.8.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7720</summary>
### Vulnerable Library - <b>node-forge-0.7.4.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- :x: **node-forge-0.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package node-forge before 0.10.0 is vulnerable to Prototype Pollution via the util.setPath function. Note: Version 0.10.0 is a breaking change removing the vulnerable functions.
<p>Publish Date: 2020-09-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7720>CVE-2020-7720</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/digitalbazaar/forge/blob/master/CHANGELOG.md">https://github.com/digitalbazaar/forge/blob/master/CHANGELOG.md</a></p>
<p>Release Date: 2020-09-01</p>
<p>Fix Resolution (node-forge): 0.10.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 9.2.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> WS-2022-0008</summary>
### Vulnerable Libraries - <b>node-forge-0.10.0.tgz</b>, <b>node-forge-0.7.4.tgz</b></p>
<p>
### <b>node-forge-0.10.0.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/google-p12-pem/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- storage-2.5.0.tgz
- gcs-resumable-upload-1.1.0.tgz
- google-auth-library-3.1.2.tgz
- gtoken-2.3.3.tgz
- google-p12-pem-1.0.5.tgz
- :x: **node-forge-0.10.0.tgz** (Vulnerable Library)
### <b>node-forge-0.7.4.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- :x: **node-forge-0.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The forge.debug API had a potential prototype pollution issue if called with untrusted input. The API was only used for internal debug purposes in a safe way and never documented or advertised. It is suspected that uses of this API, if any exist, would likely not have used untrusted inputs in a vulnerable way.
<p>Publish Date: 2022-01-08
<p>URL: <a href=https://github.com/digitalbazaar/forge/commit/51228083550dde97701ac8e06c629a5184117562>WS-2022-0008</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-5rrq-pxf6-6jx5">https://github.com/advisories/GHSA-5rrq-pxf6-6jx5</a></p>
<p>Release Date: 2022-01-08</p>
<p>Fix Resolution (node-forge): 1.0.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 10.0.2</p><p>Fix Resolution (node-forge): 1.0.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 10.0.2</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-0122</summary>
### Vulnerable Libraries - <b>node-forge-0.10.0.tgz</b>, <b>node-forge-0.7.4.tgz</b></p>
<p>
### <b>node-forge-0.10.0.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/google-p12-pem/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- storage-2.5.0.tgz
- gcs-resumable-upload-1.1.0.tgz
- google-auth-library-3.1.2.tgz
- gtoken-2.3.3.tgz
- google-p12-pem-1.0.5.tgz
- :x: **node-forge-0.10.0.tgz** (Vulnerable Library)
### <b>node-forge-0.7.4.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- :x: **node-forge-0.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
forge is vulnerable to URL Redirection to Untrusted Site
<p>Publish Date: 2022-01-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0122>CVE-2022-0122</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-gf8q-jrpm-jvxq">https://github.com/advisories/GHSA-gf8q-jrpm-jvxq</a></p>
<p>Release Date: 2022-01-06</p>
<p>Fix Resolution (node-forge): 1.0.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 10.0.2</p><p>Fix Resolution (node-forge): 1.0.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 10.0.2</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-24773</summary>
### Vulnerable Libraries - <b>node-forge-0.10.0.tgz</b>, <b>node-forge-0.7.4.tgz</b></p>
<p>
### <b>node-forge-0.10.0.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/google-p12-pem/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- storage-2.5.0.tgz
- gcs-resumable-upload-1.1.0.tgz
- google-auth-library-3.1.2.tgz
- gtoken-2.3.3.tgz
- google-p12-pem-1.0.5.tgz
- :x: **node-forge-0.10.0.tgz** (Vulnerable Library)
### <b>node-forge-0.7.4.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- :x: **node-forge-0.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Forge (also called `node-forge`) is a native implementation of Transport Layer Security in JavaScript. Prior to version 1.3.0, RSA PKCS#1 v1.5 signature verification code does not properly check `DigestInfo` for a proper ASN.1 structure. This can lead to successful verification with signatures that contain invalid structures but a valid digest. The issue has been addressed in `node-forge` version 1.3.0. There are currently no known workarounds.
<p>Publish Date: 2022-03-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24773>CVE-2022-24773</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24773">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24773</a></p>
<p>Release Date: 2022-03-18</p>
<p>Fix Resolution (node-forge): 1.3.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 10.0.2</p><p>Fix Resolution (node-forge): 1.3.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 10.0.2</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-7765</summary>
### Vulnerable Library - <b>util-0.2.14.tgz</b></p>
<p>_NOTE: This is specifically tailored for Firebase JS SDK usage, if you are not a member of the Firebase team, please avoid using this package_</p>
<p>Library home page: <a href="https://registry.npmjs.org/@firebase/util/-/util-0.2.14.tgz">https://registry.npmjs.org/@firebase/util/-/util-0.2.14.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/@firebase/util/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- database-0.3.20.tgz
- :x: **util-0.2.14.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package @firebase/util before 0.3.4. This vulnerability relates to the deepExtend function within the DeepCopy.ts file. Depending on if user input is provided, an attacker can overwrite and pollute the object prototype of a program.
<p>Publish Date: 2020-11-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7765>CVE-2020-7765</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7765">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7765</a></p>
<p>Release Date: 2020-11-16</p>
<p>Fix Resolution (@firebase/util): 0.3.3-2020922203858</p>
<p>Direct dependency fix Resolution (firebase-admin): 9.4.2</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"8.8.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-26289","vulnerabilityDetails":"date-and-time is an npm package for manipulating date and time. In date-and-time before version 0.14.2, there a regular expression involved in parsing which can be exploited to to cause a denial of service. This is fixed in version 0.14.2.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26289","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"8.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-25878","vulnerabilityDetails":"The package protobufjs before 6.11.3 are vulnerable to Prototype Pollution which can allow an attacker to add/modify properties of the Object.prototype. This vulnerability can occur in multiple ways: 1. by providing untrusted user input to util.setProperty or to ReflectionObject.setParsedOption functions 2. by parsing/loading .proto files","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-25878","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"8.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7768","vulnerabilityDetails":"The package grpc before 1.24.4; the package @grpc/grpc-js before 1.1.8 are vulnerable to Prototype Pollution via loadPackageDefinition.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7768","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"dicer","packageVersion":"0.3.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"firebase-admin:7.4.0;dicer:0.3.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"no_fix","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-24434","vulnerabilityDetails":"This affects all versions of package dicer. A malicious attacker can send a modified form to server, and crash the nodejs service. An attacker could sent the payload again and again so that the service continuously crashes.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24434","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.0.2","isBinary":false},{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.0.2","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-24772","vulnerabilityDetails":"Forge (also called `node-forge`) is a native implementation of Transport Layer Security in JavaScript. Prior to version 1.3.0, RSA PKCS#1 v1.5 signature verification code does not check for tailing garbage bytes after decoding a `DigestInfo` ASN.1 structure. This can allow padding bytes to be removed and garbage data added to forge a signature when a low public exponent is being used. The issue has been addressed in `node-forge` version 1.3.0. There are currently no known workarounds.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24772","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"9.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-8237","vulnerabilityDetails":"Prototype pollution in json-bigint npm package \u003c 1.0.0 may lead to a denial-of-service (DoS) attack.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8237","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.0.2","isBinary":false},{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.0.2","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-24771","vulnerabilityDetails":"Forge (also called `node-forge`) is a native implementation of Transport Layer Security in JavaScript. Prior to version 1.3.0, RSA PKCS#1 v1.5 signature verification code is lenient in checking the digest algorithm structure. This can allow a crafted structure that steals padding bytes and uses unchecked portion of the PKCS#1 encoded message to forge a signature when a low public exponent is being used. The issue has been addressed in `node-forge` version 1.3.0. There are currently no known workarounds.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24771","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"8.8.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"WS-2020-0219","vulnerabilityDetails":"Due to an overly permissive regular expression, the parsing of certain date strings may lead to a denial of service.","vulnerabilityUrl":"https://github.com/knowledgecode/date-and-time/commit/9e4b501eacddccc8b1f559fb414f48472ee17c2a","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"9.2.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7720","vulnerabilityDetails":"The package node-forge before 0.10.0 is vulnerable to Prototype Pollution via the util.setPath function. Note: Version 0.10.0 is a breaking change removing the vulnerable functions.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7720","cvss3Severity":"high","cvss3Score":"7.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.0.2","isBinary":false},{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.0.2","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"WS-2022-0008","vulnerabilityDetails":"The forge.debug API had a potential prototype pollution issue if called with untrusted input. The API was only used for internal debug purposes in a safe way and never documented or advertised. It is suspected that uses of this API, if any exist, would likely not have used untrusted inputs in a vulnerable way.","vulnerabilityUrl":"https://github.com/digitalbazaar/forge/commit/51228083550dde97701ac8e06c629a5184117562","cvss3Severity":"medium","cvss3Score":"6.6","cvss3Metrics":{"A":"High","AC":"High","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.0.2","isBinary":false},{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.0.2","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-0122","vulnerabilityDetails":"forge is vulnerable to URL Redirection to Untrusted Site","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0122","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.0.2","isBinary":false},{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.0.2","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-24773","vulnerabilityDetails":"Forge (also called `node-forge`) is a native implementation of Transport Layer Security in JavaScript. Prior to version 1.3.0, RSA PKCS#1 v1.5 signature verification code does not properly check `DigestInfo` for a proper ASN.1 structure. This can lead to successful verification with signatures that contain invalid structures but a valid digest. The issue has been addressed in `node-forge` version 1.3.0. There are currently no known workarounds.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24773","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"9.4.2","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7765","vulnerabilityDetails":"This affects the package @firebase/util before 0.3.4. This vulnerability relates to the deepExtend function within the DeepCopy.ts file. Depending on if user input is provided, an attacker can overwrite and pollute the object prototype of a program.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7765","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"Low"},"extraData":{}}]</REMEDIATE> --> | True | firebase-admin-7.4.0.tgz: 13 vulnerabilities (highest severity is: 7.5) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>firebase-admin-7.4.0.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-forge/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2020-26289](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26289) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | date-and-time-0.6.3.tgz | Transitive | 8.8.0 | ❌ |
| [CVE-2022-25878](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-25878) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | protobufjs-5.0.3.tgz | Transitive | 8.0.0 | ❌ |
| [CVE-2020-7768](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7768) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | grpc-js-0.3.6.tgz | Transitive | 8.0.0 | ❌ |
| [CVE-2022-24434](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24434) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | dicer-0.3.1.tgz | Transitive | N/A | ❌ |
| [CVE-2022-24772](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24772) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | multiple | Transitive | 10.0.2 | ❌ |
| [CVE-2020-8237](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8237) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | json-bigint-0.3.1.tgz | Transitive | 9.0.0 | ❌ |
| [CVE-2022-24771](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24771) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | multiple | Transitive | 10.0.2 | ❌ |
| [WS-2020-0219](https://github.com/knowledgecode/date-and-time/commit/9e4b501eacddccc8b1f559fb414f48472ee17c2a) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | date-and-time-0.6.3.tgz | Transitive | 8.8.0 | ❌ |
| [CVE-2020-7720](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7720) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | node-forge-0.7.4.tgz | Transitive | 9.2.0 | ❌ |
| [WS-2022-0008](https://github.com/digitalbazaar/forge/commit/51228083550dde97701ac8e06c629a5184117562) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.6 | multiple | Transitive | 10.0.2 | ❌ |
| [CVE-2022-0122](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0122) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | multiple | Transitive | 10.0.2 | ❌ |
| [CVE-2022-24773](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24773) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | multiple | Transitive | 10.0.2 | ❌ |
| [CVE-2020-7765](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7765) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | util-0.2.14.tgz | Transitive | 9.4.2 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-26289</summary>
### Vulnerable Library - <b>date-and-time-0.6.3.tgz</b></p>
<p>A Minimalist DateTime utility for Node.js and the browser</p>
<p>Library home page: <a href="https://registry.npmjs.org/date-and-time/-/date-and-time-0.6.3.tgz">https://registry.npmjs.org/date-and-time/-/date-and-time-0.6.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/date-and-time/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- storage-2.5.0.tgz
- :x: **date-and-time-0.6.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
date-and-time is an npm package for manipulating date and time. In date-and-time before version 0.14.2, there a regular expression involved in parsing which can be exploited to to cause a denial of service. This is fixed in version 0.14.2.
<p>Publish Date: 2020-12-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26289>CVE-2020-26289</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-26289">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-26289</a></p>
<p>Release Date: 2020-12-28</p>
<p>Fix Resolution (date-and-time): 0.14.2</p>
<p>Direct dependency fix Resolution (firebase-admin): 8.8.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-25878</summary>
### Vulnerable Library - <b>protobufjs-5.0.3.tgz</b></p>
<p>Protocol Buffers for JavaScript. Finally.</p>
<p>Library home page: <a href="https://registry.npmjs.org/protobufjs/-/protobufjs-5.0.3.tgz">https://registry.npmjs.org/protobufjs/-/protobufjs-5.0.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/protobufjs/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- firestore-1.3.0.tgz
- google-gax-0.25.6.tgz
- grpc-1.24.11.tgz
- :x: **protobufjs-5.0.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package protobufjs before 6.11.3 are vulnerable to Prototype Pollution which can allow an attacker to add/modify properties of the Object.prototype. This vulnerability can occur in multiple ways: 1. by providing untrusted user input to util.setProperty or to ReflectionObject.setParsedOption functions 2. by parsing/loading .proto files
<p>Publish Date: 2022-05-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-25878>CVE-2022-25878</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25878">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25878</a></p>
<p>Release Date: 2022-05-27</p>
<p>Fix Resolution (protobufjs): 6.11.3</p>
<p>Direct dependency fix Resolution (firebase-admin): 8.0.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7768</summary>
### Vulnerable Library - <b>grpc-js-0.3.6.tgz</b></p>
<p>gRPC Library for Node - pure JS implementation</p>
<p>Library home page: <a href="https://registry.npmjs.org/@grpc/grpc-js/-/grpc-js-0.3.6.tgz">https://registry.npmjs.org/@grpc/grpc-js/-/grpc-js-0.3.6.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/google-gax/node_modules/@grpc/grpc-js/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- firestore-1.3.0.tgz
- google-gax-0.25.6.tgz
- :x: **grpc-js-0.3.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package grpc before 1.24.4; the package @grpc/grpc-js before 1.1.8 are vulnerable to Prototype Pollution via loadPackageDefinition.
<p>Publish Date: 2020-11-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7768>CVE-2020-7768</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7768">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7768</a></p>
<p>Release Date: 2020-11-11</p>
<p>Fix Resolution (@grpc/grpc-js): 1.1.8</p>
<p>Direct dependency fix Resolution (firebase-admin): 8.0.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-24434</summary>
### Vulnerable Library - <b>dicer-0.3.1.tgz</b></p>
<p>A very fast streaming multipart parser for node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/dicer/-/dicer-0.3.1.tgz">https://registry.npmjs.org/dicer/-/dicer-0.3.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/dicer/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- :x: **dicer-0.3.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects all versions of package dicer. A malicious attacker can send a modified form to server, and crash the nodejs service. An attacker could sent the payload again and again so that the service continuously crashes.
<p>Publish Date: 2022-05-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24434>CVE-2022-24434</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2022-24434">https://nvd.nist.gov/vuln/detail/CVE-2022-24434</a></p>
<p>Release Date: 2022-05-20</p>
<p>Fix Resolution: no_fix</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-24772</summary>
### Vulnerable Libraries - <b>node-forge-0.10.0.tgz</b>, <b>node-forge-0.7.4.tgz</b></p>
<p>
### <b>node-forge-0.10.0.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/google-p12-pem/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- storage-2.5.0.tgz
- gcs-resumable-upload-1.1.0.tgz
- google-auth-library-3.1.2.tgz
- gtoken-2.3.3.tgz
- google-p12-pem-1.0.5.tgz
- :x: **node-forge-0.10.0.tgz** (Vulnerable Library)
### <b>node-forge-0.7.4.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- :x: **node-forge-0.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Forge (also called `node-forge`) is a native implementation of Transport Layer Security in JavaScript. Prior to version 1.3.0, RSA PKCS#1 v1.5 signature verification code does not check for tailing garbage bytes after decoding a `DigestInfo` ASN.1 structure. This can allow padding bytes to be removed and garbage data added to forge a signature when a low public exponent is being used. The issue has been addressed in `node-forge` version 1.3.0. There are currently no known workarounds.
<p>Publish Date: 2022-03-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24772>CVE-2022-24772</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24772">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24772</a></p>
<p>Release Date: 2022-03-18</p>
<p>Fix Resolution (node-forge): 1.3.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 10.0.2</p><p>Fix Resolution (node-forge): 1.3.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 10.0.2</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-8237</summary>
### Vulnerable Library - <b>json-bigint-0.3.1.tgz</b></p>
<p>JSON.parse with bigints support</p>
<p>Library home page: <a href="https://registry.npmjs.org/json-bigint/-/json-bigint-0.3.1.tgz">https://registry.npmjs.org/json-bigint/-/json-bigint-0.3.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/json-bigint/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- storage-2.5.0.tgz
- gcs-resumable-upload-1.1.0.tgz
- google-auth-library-3.1.2.tgz
- gcp-metadata-1.0.0.tgz
- :x: **json-bigint-0.3.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Prototype pollution in json-bigint npm package < 1.0.0 may lead to a denial-of-service (DoS) attack.
<p>Publish Date: 2020-09-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8237>CVE-2020-8237</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://hackerone.com/reports/916430">https://hackerone.com/reports/916430</a></p>
<p>Release Date: 2020-09-30</p>
<p>Fix Resolution (json-bigint): 1.0.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 9.0.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-24771</summary>
### Vulnerable Libraries - <b>node-forge-0.10.0.tgz</b>, <b>node-forge-0.7.4.tgz</b></p>
<p>
### <b>node-forge-0.10.0.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/google-p12-pem/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- storage-2.5.0.tgz
- gcs-resumable-upload-1.1.0.tgz
- google-auth-library-3.1.2.tgz
- gtoken-2.3.3.tgz
- google-p12-pem-1.0.5.tgz
- :x: **node-forge-0.10.0.tgz** (Vulnerable Library)
### <b>node-forge-0.7.4.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- :x: **node-forge-0.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Forge (also called `node-forge`) is a native implementation of Transport Layer Security in JavaScript. Prior to version 1.3.0, RSA PKCS#1 v1.5 signature verification code is lenient in checking the digest algorithm structure. This can allow a crafted structure that steals padding bytes and uses unchecked portion of the PKCS#1 encoded message to forge a signature when a low public exponent is being used. The issue has been addressed in `node-forge` version 1.3.0. There are currently no known workarounds.
<p>Publish Date: 2022-03-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24771>CVE-2022-24771</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24771">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24771</a></p>
<p>Release Date: 2022-03-18</p>
<p>Fix Resolution (node-forge): 1.3.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 10.0.2</p><p>Fix Resolution (node-forge): 1.3.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 10.0.2</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2020-0219</summary>
### Vulnerable Library - <b>date-and-time-0.6.3.tgz</b></p>
<p>A Minimalist DateTime utility for Node.js and the browser</p>
<p>Library home page: <a href="https://registry.npmjs.org/date-and-time/-/date-and-time-0.6.3.tgz">https://registry.npmjs.org/date-and-time/-/date-and-time-0.6.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/date-and-time/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- storage-2.5.0.tgz
- :x: **date-and-time-0.6.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Due to an overly permissive regular expression, the parsing of certain date strings may lead to a denial of service.
<p>Publish Date: 2020-12-25
<p>URL: <a href=https://github.com/knowledgecode/date-and-time/commit/9e4b501eacddccc8b1f559fb414f48472ee17c2a>WS-2020-0219</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/knowledgecode/date-and-time/releases/tag/v0.14.2">https://github.com/knowledgecode/date-and-time/releases/tag/v0.14.2</a></p>
<p>Release Date: 2020-12-25</p>
<p>Fix Resolution (date-and-time): 0.14.2</p>
<p>Direct dependency fix Resolution (firebase-admin): 8.8.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7720</summary>
### Vulnerable Library - <b>node-forge-0.7.4.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- :x: **node-forge-0.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package node-forge before 0.10.0 is vulnerable to Prototype Pollution via the util.setPath function. Note: Version 0.10.0 is a breaking change removing the vulnerable functions.
<p>Publish Date: 2020-09-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7720>CVE-2020-7720</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/digitalbazaar/forge/blob/master/CHANGELOG.md">https://github.com/digitalbazaar/forge/blob/master/CHANGELOG.md</a></p>
<p>Release Date: 2020-09-01</p>
<p>Fix Resolution (node-forge): 0.10.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 9.2.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> WS-2022-0008</summary>
### Vulnerable Libraries - <b>node-forge-0.10.0.tgz</b>, <b>node-forge-0.7.4.tgz</b></p>
<p>
### <b>node-forge-0.10.0.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/google-p12-pem/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- storage-2.5.0.tgz
- gcs-resumable-upload-1.1.0.tgz
- google-auth-library-3.1.2.tgz
- gtoken-2.3.3.tgz
- google-p12-pem-1.0.5.tgz
- :x: **node-forge-0.10.0.tgz** (Vulnerable Library)
### <b>node-forge-0.7.4.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- :x: **node-forge-0.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The forge.debug API had a potential prototype pollution issue if called with untrusted input. The API was only used for internal debug purposes in a safe way and never documented or advertised. It is suspected that uses of this API, if any exist, would likely not have used untrusted inputs in a vulnerable way.
<p>Publish Date: 2022-01-08
<p>URL: <a href=https://github.com/digitalbazaar/forge/commit/51228083550dde97701ac8e06c629a5184117562>WS-2022-0008</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-5rrq-pxf6-6jx5">https://github.com/advisories/GHSA-5rrq-pxf6-6jx5</a></p>
<p>Release Date: 2022-01-08</p>
<p>Fix Resolution (node-forge): 1.0.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 10.0.2</p><p>Fix Resolution (node-forge): 1.0.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 10.0.2</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-0122</summary>
### Vulnerable Libraries - <b>node-forge-0.10.0.tgz</b>, <b>node-forge-0.7.4.tgz</b></p>
<p>
### <b>node-forge-0.10.0.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/google-p12-pem/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- storage-2.5.0.tgz
- gcs-resumable-upload-1.1.0.tgz
- google-auth-library-3.1.2.tgz
- gtoken-2.3.3.tgz
- google-p12-pem-1.0.5.tgz
- :x: **node-forge-0.10.0.tgz** (Vulnerable Library)
### <b>node-forge-0.7.4.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- :x: **node-forge-0.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
forge is vulnerable to URL Redirection to Untrusted Site
<p>Publish Date: 2022-01-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0122>CVE-2022-0122</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-gf8q-jrpm-jvxq">https://github.com/advisories/GHSA-gf8q-jrpm-jvxq</a></p>
<p>Release Date: 2022-01-06</p>
<p>Fix Resolution (node-forge): 1.0.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 10.0.2</p><p>Fix Resolution (node-forge): 1.0.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 10.0.2</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-24773</summary>
### Vulnerable Libraries - <b>node-forge-0.10.0.tgz</b>, <b>node-forge-0.7.4.tgz</b></p>
<p>
### <b>node-forge-0.10.0.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/google-p12-pem/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- storage-2.5.0.tgz
- gcs-resumable-upload-1.1.0.tgz
- google-auth-library-3.1.2.tgz
- gtoken-2.3.3.tgz
- google-p12-pem-1.0.5.tgz
- :x: **node-forge-0.10.0.tgz** (Vulnerable Library)
### <b>node-forge-0.7.4.tgz</b></p>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.7.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- :x: **node-forge-0.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Forge (also called `node-forge`) is a native implementation of Transport Layer Security in JavaScript. Prior to version 1.3.0, RSA PKCS#1 v1.5 signature verification code does not properly check `DigestInfo` for a proper ASN.1 structure. This can lead to successful verification with signatures that contain invalid structures but a valid digest. The issue has been addressed in `node-forge` version 1.3.0. There are currently no known workarounds.
<p>Publish Date: 2022-03-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24773>CVE-2022-24773</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24773">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24773</a></p>
<p>Release Date: 2022-03-18</p>
<p>Fix Resolution (node-forge): 1.3.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 10.0.2</p><p>Fix Resolution (node-forge): 1.3.0</p>
<p>Direct dependency fix Resolution (firebase-admin): 10.0.2</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-7765</summary>
### Vulnerable Library - <b>util-0.2.14.tgz</b></p>
<p>_NOTE: This is specifically tailored for Firebase JS SDK usage, if you are not a member of the Firebase team, please avoid using this package_</p>
<p>Library home page: <a href="https://registry.npmjs.org/@firebase/util/-/util-0.2.14.tgz">https://registry.npmjs.org/@firebase/util/-/util-0.2.14.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/@firebase/util/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-7.4.0.tgz (Root Library)
- database-0.3.20.tgz
- :x: **util-0.2.14.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/coreui-website-update/commit/0f8e354612545df2de46d3013620a08c3d1079f0">0f8e354612545df2de46d3013620a08c3d1079f0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package @firebase/util before 0.3.4. This vulnerability relates to the deepExtend function within the DeepCopy.ts file. Depending on if user input is provided, an attacker can overwrite and pollute the object prototype of a program.
<p>Publish Date: 2020-11-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7765>CVE-2020-7765</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7765">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7765</a></p>
<p>Release Date: 2020-11-16</p>
<p>Fix Resolution (@firebase/util): 0.3.3-2020922203858</p>
<p>Direct dependency fix Resolution (firebase-admin): 9.4.2</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"8.8.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-26289","vulnerabilityDetails":"date-and-time is an npm package for manipulating date and time. In date-and-time before version 0.14.2, there a regular expression involved in parsing which can be exploited to to cause a denial of service. This is fixed in version 0.14.2.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26289","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"8.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-25878","vulnerabilityDetails":"The package protobufjs before 6.11.3 are vulnerable to Prototype Pollution which can allow an attacker to add/modify properties of the Object.prototype. This vulnerability can occur in multiple ways: 1. by providing untrusted user input to util.setProperty or to ReflectionObject.setParsedOption functions 2. by parsing/loading .proto files","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-25878","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"8.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7768","vulnerabilityDetails":"The package grpc before 1.24.4; the package @grpc/grpc-js before 1.1.8 are vulnerable to Prototype Pollution via loadPackageDefinition.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7768","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"dicer","packageVersion":"0.3.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"firebase-admin:7.4.0;dicer:0.3.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"no_fix","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-24434","vulnerabilityDetails":"This affects all versions of package dicer. A malicious attacker can send a modified form to server, and crash the nodejs service. An attacker could sent the payload again and again so that the service continuously crashes.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24434","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.0.2","isBinary":false},{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.0.2","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-24772","vulnerabilityDetails":"Forge (also called `node-forge`) is a native implementation of Transport Layer Security in JavaScript. Prior to version 1.3.0, RSA PKCS#1 v1.5 signature verification code does not check for tailing garbage bytes after decoding a `DigestInfo` ASN.1 structure. This can allow padding bytes to be removed and garbage data added to forge a signature when a low public exponent is being used. The issue has been addressed in `node-forge` version 1.3.0. There are currently no known workarounds.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24772","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"9.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-8237","vulnerabilityDetails":"Prototype pollution in json-bigint npm package \u003c 1.0.0 may lead to a denial-of-service (DoS) attack.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8237","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.0.2","isBinary":false},{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.0.2","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-24771","vulnerabilityDetails":"Forge (also called `node-forge`) is a native implementation of Transport Layer Security in JavaScript. Prior to version 1.3.0, RSA PKCS#1 v1.5 signature verification code is lenient in checking the digest algorithm structure. This can allow a crafted structure that steals padding bytes and uses unchecked portion of the PKCS#1 encoded message to forge a signature when a low public exponent is being used. The issue has been addressed in `node-forge` version 1.3.0. There are currently no known workarounds.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24771","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"8.8.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"WS-2020-0219","vulnerabilityDetails":"Due to an overly permissive regular expression, the parsing of certain date strings may lead to a denial of service.","vulnerabilityUrl":"https://github.com/knowledgecode/date-and-time/commit/9e4b501eacddccc8b1f559fb414f48472ee17c2a","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"9.2.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7720","vulnerabilityDetails":"The package node-forge before 0.10.0 is vulnerable to Prototype Pollution via the util.setPath function. Note: Version 0.10.0 is a breaking change removing the vulnerable functions.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7720","cvss3Severity":"high","cvss3Score":"7.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.0.2","isBinary":false},{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.0.2","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"WS-2022-0008","vulnerabilityDetails":"The forge.debug API had a potential prototype pollution issue if called with untrusted input. The API was only used for internal debug purposes in a safe way and never documented or advertised. It is suspected that uses of this API, if any exist, would likely not have used untrusted inputs in a vulnerable way.","vulnerabilityUrl":"https://github.com/digitalbazaar/forge/commit/51228083550dde97701ac8e06c629a5184117562","cvss3Severity":"medium","cvss3Score":"6.6","cvss3Metrics":{"A":"High","AC":"High","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.0.2","isBinary":false},{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.0.2","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-0122","vulnerabilityDetails":"forge is vulnerable to URL Redirection to Untrusted Site","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0122","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.0.2","isBinary":false},{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.0.2","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-24773","vulnerabilityDetails":"Forge (also called `node-forge`) is a native implementation of Transport Layer Security in JavaScript. Prior to version 1.3.0, RSA PKCS#1 v1.5 signature verification code does not properly check `DigestInfo` for a proper ASN.1 structure. This can lead to successful verification with signatures that contain invalid structures but a valid digest. The issue has been addressed in `node-forge` version 1.3.0. There are currently no known workarounds.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24773","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"firebase-admin","packageVersion":"7.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"firebase-admin:7.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"9.4.2","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7765","vulnerabilityDetails":"This affects the package @firebase/util before 0.3.4. This vulnerability relates to the deepExtend function within the DeepCopy.ts file. Depending on if user input is provided, an attacker can overwrite and pollute the object prototype of a program.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7765","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"Low"},"extraData":{}}]</REMEDIATE> --> | non_defect | firebase admin tgz vulnerabilities highest severity is autoclosed vulnerable library firebase admin tgz path to dependency file package json path to vulnerable library node modules node forge package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high date and time tgz transitive high protobufjs tgz transitive high grpc js tgz transitive high dicer tgz transitive n a high multiple transitive high json bigint tgz transitive high multiple transitive high date and time tgz transitive high node forge tgz transitive medium multiple transitive medium multiple transitive medium multiple transitive medium util tgz transitive details cve vulnerable library date and time tgz a minimalist datetime utility for node js and the browser library home page a href path to dependency file package json path to vulnerable library node modules date and time package json dependency hierarchy firebase admin tgz root library storage tgz x date and time tgz vulnerable library found in head commit a href found in base branch master vulnerability details date and time is an npm package for manipulating date and time in date and time before version there a regular expression involved in parsing which can be exploited to to cause a denial of service this is fixed in version publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution date and time direct dependency fix resolution firebase admin step up your open source security game with mend cve vulnerable library protobufjs tgz protocol buffers for javascript finally library home page a href path to dependency file package json path to vulnerable library node modules protobufjs package json dependency hierarchy firebase admin tgz root library firestore tgz google gax tgz grpc tgz x protobufjs tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package protobufjs before are vulnerable to prototype pollution which can allow an attacker to add modify properties of the object prototype this vulnerability can occur in multiple ways by providing untrusted user input to util setproperty or to reflectionobject setparsedoption functions by parsing loading proto files publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution protobufjs direct dependency fix resolution firebase admin step up your open source security game with mend cve vulnerable library grpc js tgz grpc library for node pure js implementation library home page a href path to dependency file package json path to vulnerable library node modules google gax node modules grpc grpc js package json dependency hierarchy firebase admin tgz root library firestore tgz google gax tgz x grpc js tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package grpc before the package grpc grpc js before are vulnerable to prototype pollution via loadpackagedefinition publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution grpc grpc js direct dependency fix resolution firebase admin step up your open source security game with mend cve vulnerable library dicer tgz a very fast streaming multipart parser for node js library home page a href path to dependency file package json path to vulnerable library node modules dicer package json dependency hierarchy firebase admin tgz root library x dicer tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects all versions of package dicer a malicious attacker can send a modified form to server and crash the nodejs service an attacker could sent the payload again and again so that the service continuously crashes publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution no fix step up your open source security game with mend cve vulnerable libraries node forge tgz node forge tgz node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file package json path to vulnerable library node modules google pem node modules node forge package json dependency hierarchy firebase admin tgz root library storage tgz gcs resumable upload tgz google auth library tgz gtoken tgz google pem tgz x node forge tgz vulnerable library node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file package json path to vulnerable library node modules node forge package json dependency hierarchy firebase admin tgz root library x node forge tgz vulnerable library found in head commit a href found in base branch master vulnerability details forge also called node forge is a native implementation of transport layer security in javascript prior to version rsa pkcs signature verification code does not check for tailing garbage bytes after decoding a digestinfo asn structure this can allow padding bytes to be removed and garbage data added to forge a signature when a low public exponent is being used the issue has been addressed in node forge version there are currently no known workarounds publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution node forge direct dependency fix resolution firebase admin fix resolution node forge direct dependency fix resolution firebase admin step up your open source security game with mend cve vulnerable library json bigint tgz json parse with bigints support library home page a href path to dependency file package json path to vulnerable library node modules json bigint package json dependency hierarchy firebase admin tgz root library storage tgz gcs resumable upload tgz google auth library tgz gcp metadata tgz x json bigint tgz vulnerable library found in head commit a href found in base branch master vulnerability details prototype pollution in json bigint npm package may lead to a denial of service dos attack publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution json bigint direct dependency fix resolution firebase admin step up your open source security game with mend cve vulnerable libraries node forge tgz node forge tgz node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file package json path to vulnerable library node modules google pem node modules node forge package json dependency hierarchy firebase admin tgz root library storage tgz gcs resumable upload tgz google auth library tgz gtoken tgz google pem tgz x node forge tgz vulnerable library node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file package json path to vulnerable library node modules node forge package json dependency hierarchy firebase admin tgz root library x node forge tgz vulnerable library found in head commit a href found in base branch master vulnerability details forge also called node forge is a native implementation of transport layer security in javascript prior to version rsa pkcs signature verification code is lenient in checking the digest algorithm structure this can allow a crafted structure that steals padding bytes and uses unchecked portion of the pkcs encoded message to forge a signature when a low public exponent is being used the issue has been addressed in node forge version there are currently no known workarounds publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution node forge direct dependency fix resolution firebase admin fix resolution node forge direct dependency fix resolution firebase admin step up your open source security game with mend ws vulnerable library date and time tgz a minimalist datetime utility for node js and the browser library home page a href path to dependency file package json path to vulnerable library node modules date and time package json dependency hierarchy firebase admin tgz root library storage tgz x date and time tgz vulnerable library found in head commit a href found in base branch master vulnerability details due to an overly permissive regular expression the parsing of certain date strings may lead to a denial of service publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution date and time direct dependency fix resolution firebase admin step up your open source security game with mend cve vulnerable library node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file package json path to vulnerable library node modules node forge package json dependency hierarchy firebase admin tgz root library x node forge tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package node forge before is vulnerable to prototype pollution via the util setpath function note version is a breaking change removing the vulnerable functions publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution node forge direct dependency fix resolution firebase admin step up your open source security game with mend ws vulnerable libraries node forge tgz node forge tgz node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file package json path to vulnerable library node modules google pem node modules node forge package json dependency hierarchy firebase admin tgz root library storage tgz gcs resumable upload tgz google auth library tgz gtoken tgz google pem tgz x node forge tgz vulnerable library node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file package json path to vulnerable library node modules node forge package json dependency hierarchy firebase admin tgz root library x node forge tgz vulnerable library found in head commit a href found in base branch master vulnerability details the forge debug api had a potential prototype pollution issue if called with untrusted input the api was only used for internal debug purposes in a safe way and never documented or advertised it is suspected that uses of this api if any exist would likely not have used untrusted inputs in a vulnerable way publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution node forge direct dependency fix resolution firebase admin fix resolution node forge direct dependency fix resolution firebase admin step up your open source security game with mend cve vulnerable libraries node forge tgz node forge tgz node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file package json path to vulnerable library node modules google pem node modules node forge package json dependency hierarchy firebase admin tgz root library storage tgz gcs resumable upload tgz google auth library tgz gtoken tgz google pem tgz x node forge tgz vulnerable library node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file package json path to vulnerable library node modules node forge package json dependency hierarchy firebase admin tgz root library x node forge tgz vulnerable library found in head commit a href found in base branch master vulnerability details forge is vulnerable to url redirection to untrusted site publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution node forge direct dependency fix resolution firebase admin fix resolution node forge direct dependency fix resolution firebase admin step up your open source security game with mend cve vulnerable libraries node forge tgz node forge tgz node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file package json path to vulnerable library node modules google pem node modules node forge package json dependency hierarchy firebase admin tgz root library storage tgz gcs resumable upload tgz google auth library tgz gtoken tgz google pem tgz x node forge tgz vulnerable library node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file package json path to vulnerable library node modules node forge package json dependency hierarchy firebase admin tgz root library x node forge tgz vulnerable library found in head commit a href found in base branch master vulnerability details forge also called node forge is a native implementation of transport layer security in javascript prior to version rsa pkcs signature verification code does not properly check digestinfo for a proper asn structure this can lead to successful verification with signatures that contain invalid structures but a valid digest the issue has been addressed in node forge version there are currently no known workarounds publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution node forge direct dependency fix resolution firebase admin fix resolution node forge direct dependency fix resolution firebase admin step up your open source security game with mend cve vulnerable library util tgz note this is specifically tailored for firebase js sdk usage if you are not a member of the firebase team please avoid using this package library home page a href path to dependency file package json path to vulnerable library node modules firebase util package json dependency hierarchy firebase admin tgz root library database tgz x util tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package firebase util before this vulnerability relates to the deepextend function within the deepcopy ts file depending on if user input is provided an attacker can overwrite and pollute the object prototype of a program publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution firebase util direct dependency fix resolution firebase admin step up your open source security game with mend istransitivedependency false dependencytree firebase admin isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails date and time is an npm package for manipulating date and time in date and time before version there a regular expression involved in parsing which can be exploited to to cause a denial of service this is fixed in version vulnerabilityurl istransitivedependency false dependencytree firebase admin isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the package protobufjs before are vulnerable to prototype pollution which can allow an attacker to add modify properties of the object prototype this vulnerability can occur in multiple ways by providing untrusted user input to util setproperty or to reflectionobject setparsedoption functions by parsing loading proto files vulnerabilityurl istransitivedependency false dependencytree firebase admin isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the package grpc before the package grpc grpc js before are vulnerable to prototype pollution via loadpackagedefinition vulnerabilityurl istransitivedependency true dependencytree firebase admin dicer isminimumfixversionavailable true minimumfixversion no fix isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails this affects all versions of package dicer a malicious attacker can send a modified form to server and crash the nodejs service an attacker could sent the payload again and again so that the service continuously crashes vulnerabilityurl istransitivedependency false dependencytree firebase admin isminimumfixversionavailable true minimumfixversion isbinary false packagetype javascript node js packagename firebase admin packageversion packagefilepaths istransitivedependency false dependencytree firebase admin isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails forge also called node forge is a native implementation of transport layer security in javascript prior to version rsa pkcs signature verification code does not check for tailing garbage bytes after decoding a digestinfo asn structure this can allow padding bytes to be removed and garbage data added to forge a signature when a low public exponent is being used the issue has been addressed in node forge version there are currently no known workarounds vulnerabilityurl istransitivedependency false dependencytree firebase admin isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails prototype pollution in json bigint npm package may lead to a denial of service dos attack vulnerabilityurl istransitivedependency false dependencytree firebase admin isminimumfixversionavailable true minimumfixversion isbinary false packagetype javascript node js packagename firebase admin packageversion packagefilepaths istransitivedependency false dependencytree firebase admin isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails forge also called node forge is a native implementation of transport layer security in javascript prior to version rsa pkcs signature verification code is lenient in checking the digest algorithm structure this can allow a crafted structure that steals padding bytes and uses unchecked portion of the pkcs encoded message to forge a signature when a low public exponent is being used the issue has been addressed in node forge version there are currently no known workarounds vulnerabilityurl istransitivedependency false dependencytree firebase admin isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails due to an overly permissive regular expression the parsing of certain date strings may lead to a denial of service vulnerabilityurl istransitivedependency false dependencytree firebase admin isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the package node forge before is vulnerable to prototype pollution via the util setpath function note version is a breaking change removing the vulnerable functions vulnerabilityurl istransitivedependency false dependencytree firebase admin isminimumfixversionavailable true minimumfixversion isbinary false packagetype javascript node js packagename firebase admin packageversion packagefilepaths istransitivedependency false dependencytree firebase admin isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails the forge debug api had a potential prototype pollution issue if called with untrusted input the api was only used for internal debug purposes in a safe way and never documented or advertised it is suspected that uses of this api if any exist would likely not have used untrusted inputs in a vulnerable way vulnerabilityurl istransitivedependency false dependencytree firebase admin isminimumfixversionavailable true minimumfixversion isbinary false packagetype javascript node js packagename firebase admin packageversion packagefilepaths istransitivedependency false dependencytree firebase admin isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails forge is vulnerable to url redirection to untrusted site vulnerabilityurl istransitivedependency false dependencytree firebase admin isminimumfixversionavailable true minimumfixversion isbinary false packagetype javascript node js packagename firebase admin packageversion packagefilepaths istransitivedependency false dependencytree firebase admin isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails forge also called node forge is a native implementation of transport layer security in javascript prior to version rsa pkcs signature verification code does not properly check digestinfo for a proper asn structure this can lead to successful verification with signatures that contain invalid structures but a valid digest the issue has been addressed in node forge version there are currently no known workarounds vulnerabilityurl istransitivedependency false dependencytree firebase admin isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails this affects the package firebase util before this vulnerability relates to the deepextend function within the deepcopy ts file depending on if user input is provided an attacker can overwrite and pollute the object prototype of a program vulnerabilityurl | 0 |
53,068 | 13,109,227,600 | IssuesEvent | 2020-08-04 18:17:29 | spring-projects/spring-security | https://api.github.com/repos/spring-projects/spring-security | closed | Fix snapshot build failure related to reactor-netty | in: build type: bug | The `io.projectreactor.netty:reactor-netty` module has been split into 2 modules: `reactor-netty-core` and `reactor-netty-http`. See this [comment](https://github.com/reactor/reactor-netty/issues/739#issuecomment-667047117) for details.
We should update usage of `reactor-netty` to `reactor-netty-http`.
| 1.0 | Fix snapshot build failure related to reactor-netty - The `io.projectreactor.netty:reactor-netty` module has been split into 2 modules: `reactor-netty-core` and `reactor-netty-http`. See this [comment](https://github.com/reactor/reactor-netty/issues/739#issuecomment-667047117) for details.
We should update usage of `reactor-netty` to `reactor-netty-http`.
| non_defect | fix snapshot build failure related to reactor netty the io projectreactor netty reactor netty module has been split into modules reactor netty core and reactor netty http see this for details we should update usage of reactor netty to reactor netty http | 0 |
52,617 | 13,224,865,280 | IssuesEvent | 2020-08-17 20:00:26 | icecube-trac/tix4 | https://api.github.com/repos/icecube-trac/tix4 | closed | cmake goodies from trunk for V01-11-02 (Trac #66) | Migrated from Trac defect offline-software | esp. stuff from rev https://code.icecube.wisc.edu/ticket/33235 (svn info in ENGLISH, por favor)
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/66">https://code.icecube.wisc.edu/projects/icecube/ticket/66</a>, reported by blaufuss</summary>
<p>
```json
{
"status": "closed",
"changetime": "2007-11-11T03:51:18",
"_ts": "1194753078000000",
"description": "esp. stuff from rev #33235 (svn info in ENGLISH, por favor)",
"reporter": "blaufuss",
"cc": "",
"resolution": "fixed",
"time": "2007-06-15T03:01:29",
"component": "offline-software",
"summary": "cmake goodies from trunk for V01-11-02",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "",
"type": "defect"
}
```
</p>
</details>
| 1.0 | cmake goodies from trunk for V01-11-02 (Trac #66) - esp. stuff from rev https://code.icecube.wisc.edu/ticket/33235 (svn info in ENGLISH, por favor)
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/66">https://code.icecube.wisc.edu/projects/icecube/ticket/66</a>, reported by blaufuss</summary>
<p>
```json
{
"status": "closed",
"changetime": "2007-11-11T03:51:18",
"_ts": "1194753078000000",
"description": "esp. stuff from rev #33235 (svn info in ENGLISH, por favor)",
"reporter": "blaufuss",
"cc": "",
"resolution": "fixed",
"time": "2007-06-15T03:01:29",
"component": "offline-software",
"summary": "cmake goodies from trunk for V01-11-02",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "",
"type": "defect"
}
```
</p>
</details>
| defect | cmake goodies from trunk for trac esp stuff from rev svn info in english por favor migrated from json status closed changetime ts description esp stuff from rev svn info in english por favor reporter blaufuss cc resolution fixed time component offline software summary cmake goodies from trunk for priority normal keywords milestone owner type defect | 1 |
361,277 | 10,706,753,800 | IssuesEvent | 2019-10-24 15:59:04 | ArctosDB/arctos | https://api.github.com/repos/ArctosDB/arctos | closed | Other Locality IDs | Function-Locality/Event/Georeferencing Priority-High | **Proposed new value**
I would like to see a way to include additional locality identifiers.
**Definition**
Name, ID, Or Number other than Locality Nickname that has been used to identify this locality.
**Context**
There are some existing fields where this type of data has been put:
Verbatim locality is a collecting event field. Identifiers that are static through time and refer to the place and not the event should be associated with locality.
Other IDs apply to specimens, not localities. I realize that there is a Locality ID under Other ID, but why, other than legacy data structure issues, would you put locality level data in a specimen field?
**Example**
NMMNH L-6260
Our primary key locality number that I would put under Locality Nickname.
Other IDs for this same locality
UALP 75106
The primary key that the University of Arizona Laboratory of Paleontology used for this locality before we acquired the collection.
LLJ 13-75
The field number given to the site. Arguably this belongs in collection event, however for the last 30+ years our curators and collectors have used these to refer to the locality itself, not a single collecting event or set of collecting events.
Taylor's Mound
The name that people call the site.
All of these IDs are things that I need to see when I pull up the locality record. I shouldn't have to dive into the collecting events or specimens to find them. | 1.0 | Other Locality IDs - **Proposed new value**
I would like to see a way to include additional locality identifiers.
**Definition**
Name, ID, Or Number other than Locality Nickname that has been used to identify this locality.
**Context**
There are some existing fields where this type of data has been put:
Verbatim locality is a collecting event field. Identifiers that are static through time and refer to the place and not the event should be associated with locality.
Other IDs apply to specimens, not localities. I realize that there is a Locality ID under Other ID, but why, other than legacy data structure issues, would you put locality level data in a specimen field?
**Example**
NMMNH L-6260
Our primary key locality number that I would put under Locality Nickname.
Other IDs for this same locality
UALP 75106
The primary key that the University of Arizona Laboratory of Paleontology used for this locality before we acquired the collection.
LLJ 13-75
The field number given to the site. Arguably this belongs in collection event, however for the last 30+ years our curators and collectors have used these to refer to the locality itself, not a single collecting event or set of collecting events.
Taylor's Mound
The name that people call the site.
All of these IDs are things that I need to see when I pull up the locality record. I shouldn't have to dive into the collecting events or specimens to find them. | non_defect | other locality ids proposed new value i would like to see a way to include additional locality identifiers definition name id or number other than locality nickname that has been used to identify this locality context there are some existing fields where this type of data has been put verbatim locality is a collecting event field identifiers that are static through time and refer to the place and not the event should be associated with locality other ids apply to specimens not localities i realize that there is a locality id under other id but why other than legacy data structure issues would you put locality level data in a specimen field example nmmnh l our primary key locality number that i would put under locality nickname other ids for this same locality ualp the primary key that the university of arizona laboratory of paleontology used for this locality before we acquired the collection llj the field number given to the site arguably this belongs in collection event however for the last years our curators and collectors have used these to refer to the locality itself not a single collecting event or set of collecting events taylor s mound the name that people call the site all of these ids are things that i need to see when i pull up the locality record i shouldn t have to dive into the collecting events or specimens to find them | 0 |
163,380 | 6,197,448,656 | IssuesEvent | 2017-07-05 16:50:14 | openshift/origin | https://api.github.com/repos/openshift/origin | opened | Add more context in deployment logs | component/deployments kind/enhancement priority/P2 | Like when an app pod is crashlooping or the image cannot be pulled.
@mfojtik @tnozicka @smarterclayton | 1.0 | Add more context in deployment logs - Like when an app pod is crashlooping or the image cannot be pulled.
@mfojtik @tnozicka @smarterclayton | non_defect | add more context in deployment logs like when an app pod is crashlooping or the image cannot be pulled mfojtik tnozicka smarterclayton | 0 |
420,022 | 12,231,652,189 | IssuesEvent | 2020-05-04 08:12:46 | m0skit0/hms-sdk-unity | https://api.github.com/repos/m0skit0/hms-sdk-unity | opened | NullObjectReference when printing AuthHuaweiId | bug high priority | `NullReferenceException: Object reference not set to an instance of an object
at HuaweiMobileServices.Utils.AndroidJavaObjectExtensions.AsString (UnityEngine.AndroidJavaObject javaString) [0x0000b] in <79c9a00a9e864f749496b4caf8f3e43f>:0
at HuaweiMobileServices.Id.AuthHuaweiId.get_Uid () [0x00015] in <79c9a00a9e864f749496b4caf8f3e43f>:0
at StartScript.PrintAccount (HuaweiMobileServices.Id.AuthHuaweiId account) [0x00000] in <cae6ea9c16dc47fe865ee14c18f8ff7b>:0
at StartScript.OnSuccess (HuaweiMobileServices.Id.AuthHuaweiId account) [0x00019] in <cae6ea9c16dc47fe865ee14c18f8ff7b>:0
at HuaweiAccountManager.OnSignedSuccess (HuaweiMobileServices.Id.AuthHuaweiId authId) [0x00011] in <cae6ea9c16dc47fe865ee14c18f8ff7b>:0
at HuaweiMobileServices.Id.HuaweiIdAuthService+<>c__DisplayClass2_0.<StartSignIn>b__1 (HuaweiMobileServices.Id.AuthHuaweiId authHuaweiId) [0x00001] in <79c9a00a9e864f749496b4caf8f3e43f>:0
at HuaweiMobileServices.Base.OnSuccessListenerConverterWrapper`1[T].onSuccess` | 1.0 | NullObjectReference when printing AuthHuaweiId - `NullReferenceException: Object reference not set to an instance of an object
at HuaweiMobileServices.Utils.AndroidJavaObjectExtensions.AsString (UnityEngine.AndroidJavaObject javaString) [0x0000b] in <79c9a00a9e864f749496b4caf8f3e43f>:0
at HuaweiMobileServices.Id.AuthHuaweiId.get_Uid () [0x00015] in <79c9a00a9e864f749496b4caf8f3e43f>:0
at StartScript.PrintAccount (HuaweiMobileServices.Id.AuthHuaweiId account) [0x00000] in <cae6ea9c16dc47fe865ee14c18f8ff7b>:0
at StartScript.OnSuccess (HuaweiMobileServices.Id.AuthHuaweiId account) [0x00019] in <cae6ea9c16dc47fe865ee14c18f8ff7b>:0
at HuaweiAccountManager.OnSignedSuccess (HuaweiMobileServices.Id.AuthHuaweiId authId) [0x00011] in <cae6ea9c16dc47fe865ee14c18f8ff7b>:0
at HuaweiMobileServices.Id.HuaweiIdAuthService+<>c__DisplayClass2_0.<StartSignIn>b__1 (HuaweiMobileServices.Id.AuthHuaweiId authHuaweiId) [0x00001] in <79c9a00a9e864f749496b4caf8f3e43f>:0
at HuaweiMobileServices.Base.OnSuccessListenerConverterWrapper`1[T].onSuccess` | non_defect | nullobjectreference when printing authhuaweiid nullreferenceexception object reference not set to an instance of an object at huaweimobileservices utils androidjavaobjectextensions asstring unityengine androidjavaobject javastring in at huaweimobileservices id authhuaweiid get uid in at startscript printaccount huaweimobileservices id authhuaweiid account in at startscript onsuccess huaweimobileservices id authhuaweiid account in at huaweiaccountmanager onsignedsuccess huaweimobileservices id authhuaweiid authid in at huaweimobileservices id huaweiidauthservice c b huaweimobileservices id authhuaweiid authhuaweiid in at huaweimobileservices base onsuccesslistenerconverterwrapper onsuccess | 0 |
52,856 | 13,225,170,380 | IssuesEvent | 2020-08-17 20:37:52 | icecube-trac/tix4 | https://api.github.com/repos/icecube-trac/tix4 | closed | cmake gets confused on systems that have both qt4 and qt5 installed (Trac #477) | Migrated from Trac defect steamshovel | (Assigned this to nega, but not sure if he is the right guy to bother with this. We need someone who knows both about cmake and about Qt. And sjackso is leaving IceCube, unfortunately.)
My laptop has both Qt4 and Qt5 installed. When I run cmake then I see that Qt5 is found instead of Qt4. Since the include files are organized in a different way for Qt5, the build (steamshovel and glshovel, or anything else that depends on qt4) fails.
I made it work with a hack, namely by inserting the directory path where (on my system) the qt4 binaries are installed:
/usr/lib/x86_64-linux-gnu/qt4/bin
I inserted this path in cmake/tools/qt4.cmake just after the line with the keyword "PATHS" and before the line with "${I3_PORTS}/qt-4.6.0/bin".
That causes the build to complete, so now I can enjoy the functionality steamshovel again, but as already mentioned, this solution is a hack, I'm sure that there will be more users with both Qt5 and Qt4 on their systems, and it would be nice to fix it for real.
It looks like the Qt team has already foreseen this situation, because the "/usr/bin/qmake" program on my system is a symlink to /usr/bin/qtchooser, which can be called with an option -qt=qt4 or -qt=qt5 to enforce a particular Qt version. But I can't figure out where in cmake/tools/qt4.cmake (or in the CMakeLists.txt files) I could insert this. I tried adding this option setting to QT_DEFINITIONS, but that did not do anything. I failed to find out where qmake is actually called. I also checked these files:
```text
$I3_PORTS/share/cmake-2.8.5/Modules/UseQt4.cmake
/usr/share/cmake/Modules/UseQt4.cmake
```
And in neither of them I could find something that I recognized as something that would let me enforce qt4 in a meaningful way.
There probably more routes to try, but I'm running out of time, hence I'm dumping my findings so far in this ticket.
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/477">https://code.icecube.wisc.edu/projects/icecube/ticket/477</a>, reported by boersmaand owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-01-11T23:10:47",
"_ts": "1547248247244836",
"description": "(Assigned this to nega, but not sure if he is the right guy to bother with this. We need someone who knows both about cmake and about Qt. And sjackso is leaving IceCube, unfortunately.)\n\nMy laptop has both Qt4 and Qt5 installed. When I run cmake then I see that Qt5 is found instead of Qt4. Since the include files are organized in a different way for Qt5, the build (steamshovel and glshovel, or anything else that depends on qt4) fails.\n\nI made it work with a hack, namely by inserting the directory path where (on my system) the qt4 binaries are installed:\n\n/usr/lib/x86_64-linux-gnu/qt4/bin\n\nI inserted this path in cmake/tools/qt4.cmake just after the line with the keyword \"PATHS\" and before the line with \"${I3_PORTS}/qt-4.6.0/bin\".\n\nThat causes the build to complete, so now I can enjoy the functionality steamshovel again, but as already mentioned, this solution is a hack, I'm sure that there will be more users with both Qt5 and Qt4 on their systems, and it would be nice to fix it for real.\n\nIt looks like the Qt team has already foreseen this situation, because the \"/usr/bin/qmake\" program on my system is a symlink to /usr/bin/qtchooser, which can be called with an option -qt=qt4 or -qt=qt5 to enforce a particular Qt version. But I can't figure out where in cmake/tools/qt4.cmake (or in the CMakeLists.txt files) I could insert this. I tried adding this option setting to QT_DEFINITIONS, but that did not do anything. I failed to find out where qmake is actually called. I also checked these files:\n\n{{{\n$I3_PORTS/share/cmake-2.8.5/Modules/UseQt4.cmake\n/usr/share/cmake/Modules/UseQt4.cmake\n}}}\n\nAnd in neither of them I could find something that I recognized as something that would let me enforce qt4 in a meaningful way.\n\nThere probably more routes to try, but I'm running out of time, hence I'm dumping my findings so far in this ticket.",
"reporter": "boersma",
"cc": "steve.jackson@icecube.wisc.edu, david.schultz@icecube.wisc.edu",
"resolution": "fixed",
"time": "2013-12-18T11:42:15",
"component": "steamshovel",
"summary": "cmake gets confused on systems that have both qt4 and qt5 installed",
"priority": "normal",
"keywords": "qt4 cmake steamshovel glshovel",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
| 1.0 | cmake gets confused on systems that have both qt4 and qt5 installed (Trac #477) - (Assigned this to nega, but not sure if he is the right guy to bother with this. We need someone who knows both about cmake and about Qt. And sjackso is leaving IceCube, unfortunately.)
My laptop has both Qt4 and Qt5 installed. When I run cmake then I see that Qt5 is found instead of Qt4. Since the include files are organized in a different way for Qt5, the build (steamshovel and glshovel, or anything else that depends on qt4) fails.
I made it work with a hack, namely by inserting the directory path where (on my system) the qt4 binaries are installed:
/usr/lib/x86_64-linux-gnu/qt4/bin
I inserted this path in cmake/tools/qt4.cmake just after the line with the keyword "PATHS" and before the line with "${I3_PORTS}/qt-4.6.0/bin".
That causes the build to complete, so now I can enjoy the functionality steamshovel again, but as already mentioned, this solution is a hack, I'm sure that there will be more users with both Qt5 and Qt4 on their systems, and it would be nice to fix it for real.
It looks like the Qt team has already foreseen this situation, because the "/usr/bin/qmake" program on my system is a symlink to /usr/bin/qtchooser, which can be called with an option -qt=qt4 or -qt=qt5 to enforce a particular Qt version. But I can't figure out where in cmake/tools/qt4.cmake (or in the CMakeLists.txt files) I could insert this. I tried adding this option setting to QT_DEFINITIONS, but that did not do anything. I failed to find out where qmake is actually called. I also checked these files:
```text
$I3_PORTS/share/cmake-2.8.5/Modules/UseQt4.cmake
/usr/share/cmake/Modules/UseQt4.cmake
```
And in neither of them I could find something that I recognized as something that would let me enforce qt4 in a meaningful way.
There probably more routes to try, but I'm running out of time, hence I'm dumping my findings so far in this ticket.
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/477">https://code.icecube.wisc.edu/projects/icecube/ticket/477</a>, reported by boersmaand owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-01-11T23:10:47",
"_ts": "1547248247244836",
"description": "(Assigned this to nega, but not sure if he is the right guy to bother with this. We need someone who knows both about cmake and about Qt. And sjackso is leaving IceCube, unfortunately.)\n\nMy laptop has both Qt4 and Qt5 installed. When I run cmake then I see that Qt5 is found instead of Qt4. Since the include files are organized in a different way for Qt5, the build (steamshovel and glshovel, or anything else that depends on qt4) fails.\n\nI made it work with a hack, namely by inserting the directory path where (on my system) the qt4 binaries are installed:\n\n/usr/lib/x86_64-linux-gnu/qt4/bin\n\nI inserted this path in cmake/tools/qt4.cmake just after the line with the keyword \"PATHS\" and before the line with \"${I3_PORTS}/qt-4.6.0/bin\".\n\nThat causes the build to complete, so now I can enjoy the functionality steamshovel again, but as already mentioned, this solution is a hack, I'm sure that there will be more users with both Qt5 and Qt4 on their systems, and it would be nice to fix it for real.\n\nIt looks like the Qt team has already foreseen this situation, because the \"/usr/bin/qmake\" program on my system is a symlink to /usr/bin/qtchooser, which can be called with an option -qt=qt4 or -qt=qt5 to enforce a particular Qt version. But I can't figure out where in cmake/tools/qt4.cmake (or in the CMakeLists.txt files) I could insert this. I tried adding this option setting to QT_DEFINITIONS, but that did not do anything. I failed to find out where qmake is actually called. I also checked these files:\n\n{{{\n$I3_PORTS/share/cmake-2.8.5/Modules/UseQt4.cmake\n/usr/share/cmake/Modules/UseQt4.cmake\n}}}\n\nAnd in neither of them I could find something that I recognized as something that would let me enforce qt4 in a meaningful way.\n\nThere probably more routes to try, but I'm running out of time, hence I'm dumping my findings so far in this ticket.",
"reporter": "boersma",
"cc": "steve.jackson@icecube.wisc.edu, david.schultz@icecube.wisc.edu",
"resolution": "fixed",
"time": "2013-12-18T11:42:15",
"component": "steamshovel",
"summary": "cmake gets confused on systems that have both qt4 and qt5 installed",
"priority": "normal",
"keywords": "qt4 cmake steamshovel glshovel",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
| defect | cmake gets confused on systems that have both and installed trac assigned this to nega but not sure if he is the right guy to bother with this we need someone who knows both about cmake and about qt and sjackso is leaving icecube unfortunately my laptop has both and installed when i run cmake then i see that is found instead of since the include files are organized in a different way for the build steamshovel and glshovel or anything else that depends on fails i made it work with a hack namely by inserting the directory path where on my system the binaries are installed usr lib linux gnu bin i inserted this path in cmake tools cmake just after the line with the keyword paths and before the line with ports qt bin that causes the build to complete so now i can enjoy the functionality steamshovel again but as already mentioned this solution is a hack i m sure that there will be more users with both and on their systems and it would be nice to fix it for real it looks like the qt team has already foreseen this situation because the usr bin qmake program on my system is a symlink to usr bin qtchooser which can be called with an option qt or qt to enforce a particular qt version but i can t figure out where in cmake tools cmake or in the cmakelists txt files i could insert this i tried adding this option setting to qt definitions but that did not do anything i failed to find out where qmake is actually called i also checked these files text ports share cmake modules cmake usr share cmake modules cmake and in neither of them i could find something that i recognized as something that would let me enforce in a meaningful way there probably more routes to try but i m running out of time hence i m dumping my findings so far in this ticket migrated from json status closed changetime ts description assigned this to nega but not sure if he is the right guy to bother with this we need someone who knows both about cmake and about qt and sjackso is leaving icecube unfortunately n nmy laptop has both and installed when i run cmake then i see that is found instead of since the include files are organized in a different way for the build steamshovel and glshovel or anything else that depends on fails n ni made it work with a hack namely by inserting the directory path where on my system the binaries are installed n n usr lib linux gnu bin n ni inserted this path in cmake tools cmake just after the line with the keyword paths and before the line with ports qt bin n nthat causes the build to complete so now i can enjoy the functionality steamshovel again but as already mentioned this solution is a hack i m sure that there will be more users with both and on their systems and it would be nice to fix it for real n nit looks like the qt team has already foreseen this situation because the usr bin qmake program on my system is a symlink to usr bin qtchooser which can be called with an option qt or qt to enforce a particular qt version but i can t figure out where in cmake tools cmake or in the cmakelists txt files i could insert this i tried adding this option setting to qt definitions but that did not do anything i failed to find out where qmake is actually called i also checked these files n n n ports share cmake modules cmake n usr share cmake modules cmake n n nand in neither of them i could find something that i recognized as something that would let me enforce in a meaningful way n nthere probably more routes to try but i m running out of time hence i m dumping my findings so far in this ticket reporter boersma cc steve jackson icecube wisc edu david schultz icecube wisc edu resolution fixed time component steamshovel summary cmake gets confused on systems that have both and installed priority normal keywords cmake steamshovel glshovel milestone owner nega type defect | 1 |
810,227 | 30,231,920,640 | IssuesEvent | 2023-07-06 07:35:35 | tum-gis/sddi-ckan-k8s | https://api.github.com/repos/tum-gis/sddi-ckan-k8s | closed | Option to replace background/header image | priority: soon type: feature state: pending state: approved | ### Feature description
Is there an easy way to replace the background/header image? And, if not, it would be great to have one.
### Suggested solution
_No response_
### Code snippets
_No response_ | 1.0 | Option to replace background/header image - ### Feature description
Is there an easy way to replace the background/header image? And, if not, it would be great to have one.
### Suggested solution
_No response_
### Code snippets
_No response_ | non_defect | option to replace background header image feature description is there an easy way to replace the background header image and if not it would be great to have one suggested solution no response code snippets no response | 0 |
30,600 | 6,192,335,576 | IssuesEvent | 2017-07-05 01:05:35 | bridgedotnet/Bridge | https://api.github.com/repos/bridgedotnet/Bridge | opened | Metadata not prefixing with namespace index if custom [Name] set on an [External] class | defect | If a `[Name]` attribute is configured on an `[External]` class, the custom name value is not being prefixed with the namespace index within the reflection metadata.
### Steps To Reproduce
https://deck.net/59eb95b1f1bf57357c8987bb0660c3a4
```c#
class Test
{
public static void Main()
{
var type = typeof(MyClass);
Console.WriteLine(type.GetProperties());
}
}
class MyClass
{
internal MyApi api { get; private set; }
}
[External]
[Name("foo")]
class MyApi
{
string Name { get; }
}
```
### Expected Result
```js
// without [Name]
"rt":$n[1].MyApi
// with [Name[
$n[1].foo
```
### Actual Result
```js
// without [Name]
"rt":$n[1].MyApi
// with [Name[
"rt":foo
```
## See Also
* https://forums.bridge.net/forum/bridge-net-pro/bugs/4511-reflection-bug-external | 1.0 | Metadata not prefixing with namespace index if custom [Name] set on an [External] class - If a `[Name]` attribute is configured on an `[External]` class, the custom name value is not being prefixed with the namespace index within the reflection metadata.
### Steps To Reproduce
https://deck.net/59eb95b1f1bf57357c8987bb0660c3a4
```c#
class Test
{
public static void Main()
{
var type = typeof(MyClass);
Console.WriteLine(type.GetProperties());
}
}
class MyClass
{
internal MyApi api { get; private set; }
}
[External]
[Name("foo")]
class MyApi
{
string Name { get; }
}
```
### Expected Result
```js
// without [Name]
"rt":$n[1].MyApi
// with [Name[
$n[1].foo
```
### Actual Result
```js
// without [Name]
"rt":$n[1].MyApi
// with [Name[
"rt":foo
```
## See Also
* https://forums.bridge.net/forum/bridge-net-pro/bugs/4511-reflection-bug-external | defect | metadata not prefixing with namespace index if custom set on an class if a attribute is configured on an class the custom name value is not being prefixed with the namespace index within the reflection metadata steps to reproduce c class test public static void main var type typeof myclass console writeline type getproperties class myclass internal myapi api get private set class myapi string name get expected result js without rt n myapi with name n foo actual result js without rt n myapi with name rt foo see also | 1 |
31,277 | 6,485,342,753 | IssuesEvent | 2017-08-19 09:19:01 | cakephp/cakephp | https://api.github.com/repos/cakephp/cakephp | opened | Hash::remove() removes parent array unexpectedly when conditions given. | Defect Enhancement | When I tested #11060, I found another bug of Hash::remove().
This is a (multiple allowed):
* [x] bug
* [x] enhancement
* [ ] feature-discussion (RFC)
* CakePHP Version: 3.5.1
* Platform and Target: Non-related.
### What you did
```php
$array = [
'foo' => [
'bar' => [
'baz' => 1
],
],
];
debug( Hash::remove($array, 'foo.bar') );
debug( Hash::remove($array, 'foo.bar[baz=1]') );
```
### What happened
FIrst output:
```php
[
'foo' => []
]
```
Second output:
```php
[]
```
### What you expected to happen
FIrst output:
```php
[
'foo' => []
]
```
Second output:
```php
[
'foo' => []
]
```
This behavior seems to be intended, and tested here:
https://github.com/cakephp/cakephp/blob/668c0873986adeec2187aaf8f798d1d62306e61a/tests/TestCase/Utility/HashTest.php#L2151-L2165
But I think it is incorrect. If people want to remove the first-level elements, the path syntax should be:
```
{n}[Item.id=/\b2|\b4/]
```
Since Hash class doesn't support this syntax at the moment, I added a 'Enhancement' tag too. | 1.0 | Hash::remove() removes parent array unexpectedly when conditions given. - When I tested #11060, I found another bug of Hash::remove().
This is a (multiple allowed):
* [x] bug
* [x] enhancement
* [ ] feature-discussion (RFC)
* CakePHP Version: 3.5.1
* Platform and Target: Non-related.
### What you did
```php
$array = [
'foo' => [
'bar' => [
'baz' => 1
],
],
];
debug( Hash::remove($array, 'foo.bar') );
debug( Hash::remove($array, 'foo.bar[baz=1]') );
```
### What happened
FIrst output:
```php
[
'foo' => []
]
```
Second output:
```php
[]
```
### What you expected to happen
FIrst output:
```php
[
'foo' => []
]
```
Second output:
```php
[
'foo' => []
]
```
This behavior seems to be intended, and tested here:
https://github.com/cakephp/cakephp/blob/668c0873986adeec2187aaf8f798d1d62306e61a/tests/TestCase/Utility/HashTest.php#L2151-L2165
But I think it is incorrect. If people want to remove the first-level elements, the path syntax should be:
```
{n}[Item.id=/\b2|\b4/]
```
Since Hash class doesn't support this syntax at the moment, I added a 'Enhancement' tag too. | defect | hash remove removes parent array unexpectedly when conditions given when i tested i found another bug of hash remove this is a multiple allowed bug enhancement feature discussion rfc cakephp version platform and target non related what you did php array foo bar baz debug hash remove array foo bar debug hash remove array foo bar what happened first output php foo second output php what you expected to happen first output php foo second output php foo this behavior seems to be intended and tested here but i think it is incorrect if people want to remove the first level elements the path syntax should be n since hash class doesn t support this syntax at the moment i added a enhancement tag too | 1 |
139,603 | 12,875,998,760 | IssuesEvent | 2020-07-11 01:55:38 | alphaseinor/brianhague_dev_be | https://api.github.com/repos/alphaseinor/brianhague_dev_be | closed | need base server | documentation enhancement | just have a root endpoint
update dotenv
documentation for dotenv and installing project in readme.md file. | 1.0 | need base server - just have a root endpoint
update dotenv
documentation for dotenv and installing project in readme.md file. | non_defect | need base server just have a root endpoint update dotenv documentation for dotenv and installing project in readme md file | 0 |
52,556 | 13,224,835,140 | IssuesEvent | 2020-08-17 19:56:47 | icecube-trac/tix4 | https://api.github.com/repos/icecube-trac/tix4 | opened | [tableio/rootwriter] Root file "master tree" comes out empty (Trac #2419) | Incomplete Migration Migrated from Trac combo core defect | <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/2419">https://code.icecube.wisc.edu/projects/icecube/ticket/2419</a>, reported by kath</summary>
<p>
```json
{
"status": "closed",
"changetime": "2020-06-24T12:31:42",
"_ts": "1593001902142004",
"description": "\"rootwriter\" master tree is empty (although individual branches seem to be filled).\nThe master tree also cannot be used to access the branches through SetBranchAddress.\n\nHow to reproduce it: run the script \"book_data.py\" in rootwriter/resources/examples, like this:\n./book_data.py myoutput.root ${I3_TESTDATA}/sim/Level2_IC86.2011_corsika.010281.001664.00.i3.bz2\nThen, open up the root file with \"root myoutput.root\".\n\nTest 1:\nFullTree->GetEntries() <--- gives zero, whereas is should be 2229, which is the number of entries in the other two branches (SPEFit2 and SPEFitSimple).\n\nTest 2:\ndouble x\nFullTree->SetBranchAddress(\"SPEFit2.x\", &x)\nFullTree->GetEntry(0) <--- supposed to fill the variable \"x\" with the first value in the branch\nx <--- gives still zero, instead of a nice x-coordinate from the branch\n\nStrangely, doing this:\nFullTree->Scan(\"SPEFit2.x\") <--- correctly spits out a bunch of x-coordiantes! \n\nProblem appears in combo_stable, compiled with either py2_v3.1.1 and py3_v4.1.0.\nProblem does not appear in combo_V00-00-01.\n",
"reporter": "kath",
"cc": "",
"resolution": "fixed",
"time": "2020-03-17T21:07:03",
"component": "combo core",
"summary": "[tableio/rootwriter] Root file \"master tree\" comes out empty",
"priority": "major",
"keywords": "",
"milestone": "Autumnal Equinox 2020",
"owner": "",
"type": "defect"
}
```
</p>
</details>
| 1.0 | [tableio/rootwriter] Root file "master tree" comes out empty (Trac #2419) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/2419">https://code.icecube.wisc.edu/projects/icecube/ticket/2419</a>, reported by kath</summary>
<p>
```json
{
"status": "closed",
"changetime": "2020-06-24T12:31:42",
"_ts": "1593001902142004",
"description": "\"rootwriter\" master tree is empty (although individual branches seem to be filled).\nThe master tree also cannot be used to access the branches through SetBranchAddress.\n\nHow to reproduce it: run the script \"book_data.py\" in rootwriter/resources/examples, like this:\n./book_data.py myoutput.root ${I3_TESTDATA}/sim/Level2_IC86.2011_corsika.010281.001664.00.i3.bz2\nThen, open up the root file with \"root myoutput.root\".\n\nTest 1:\nFullTree->GetEntries() <--- gives zero, whereas is should be 2229, which is the number of entries in the other two branches (SPEFit2 and SPEFitSimple).\n\nTest 2:\ndouble x\nFullTree->SetBranchAddress(\"SPEFit2.x\", &x)\nFullTree->GetEntry(0) <--- supposed to fill the variable \"x\" with the first value in the branch\nx <--- gives still zero, instead of a nice x-coordinate from the branch\n\nStrangely, doing this:\nFullTree->Scan(\"SPEFit2.x\") <--- correctly spits out a bunch of x-coordiantes! \n\nProblem appears in combo_stable, compiled with either py2_v3.1.1 and py3_v4.1.0.\nProblem does not appear in combo_V00-00-01.\n",
"reporter": "kath",
"cc": "",
"resolution": "fixed",
"time": "2020-03-17T21:07:03",
"component": "combo core",
"summary": "[tableio/rootwriter] Root file \"master tree\" comes out empty",
"priority": "major",
"keywords": "",
"milestone": "Autumnal Equinox 2020",
"owner": "",
"type": "defect"
}
```
</p>
</details>
| defect | root file master tree comes out empty trac migrated from json status closed changetime ts description rootwriter master tree is empty although individual branches seem to be filled nthe master tree also cannot be used to access the branches through setbranchaddress n nhow to reproduce it run the script book data py in rootwriter resources examples like this n book data py myoutput root testdata sim corsika nthen open up the root file with root myoutput root n ntest nfulltree getentries setbranchaddress x x nfulltree getentry scan x correctly spits out a bunch of x coordiantes n nproblem appears in combo stable compiled with either and nproblem does not appear in combo n reporter kath cc resolution fixed time component combo core summary root file master tree comes out empty priority major keywords milestone autumnal equinox owner type defect | 1 |
334,182 | 24,407,617,836 | IssuesEvent | 2022-10-05 09:23:35 | esrlabs/northstar | https://api.github.com/repos/esrlabs/northstar | closed | Document capability handling | documentation audit_0822 | Document that handling of the `capability` settings in the manifest. Explicitly note that the settings affect the ambient caps which might be unexpected. | 1.0 | Document capability handling - Document that handling of the `capability` settings in the manifest. Explicitly note that the settings affect the ambient caps which might be unexpected. | non_defect | document capability handling document that handling of the capability settings in the manifest explicitly note that the settings affect the ambient caps which might be unexpected | 0 |
30,342 | 6,111,357,664 | IssuesEvent | 2017-06-21 16:51:20 | scholarslab/Neatline | https://api.github.com/repos/scholarslab/Neatline | closed | Drawing tools grabber z-index | defect priority-high | When something is selected, the active tool needs to be temporarily floated to the top so that it can be grabbed easily.
| 1.0 | Drawing tools grabber z-index - When something is selected, the active tool needs to be temporarily floated to the top so that it can be grabbed easily.
| defect | drawing tools grabber z index when something is selected the active tool needs to be temporarily floated to the top so that it can be grabbed easily | 1 |
182,104 | 30,795,222,814 | IssuesEvent | 2023-07-31 19:18:44 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | opened | Workshop of Devs to clarify forms system and customization | service-design | ## Purpose
We seem to be lacking in detailed feedback on how the forms system, design patterns, and customization all come into play. We could meet w/ Devs only to have them lay out their approach to this; the phases and tasks involved.
## Tasks
- [ ] Schedule workshop
- [ ] prepare questions list
- [ ] prepare Mural
- [ ] conduct session
- [ ] collect notes
- [ ] synthesize findings
## Acceptance Criteria
- [ ] findings documented
| 1.0 | Workshop of Devs to clarify forms system and customization - ## Purpose
We seem to be lacking in detailed feedback on how the forms system, design patterns, and customization all come into play. We could meet w/ Devs only to have them lay out their approach to this; the phases and tasks involved.
## Tasks
- [ ] Schedule workshop
- [ ] prepare questions list
- [ ] prepare Mural
- [ ] conduct session
- [ ] collect notes
- [ ] synthesize findings
## Acceptance Criteria
- [ ] findings documented
| non_defect | workshop of devs to clarify forms system and customization purpose we seem to be lacking in detailed feedback on how the forms system design patterns and customization all come into play we could meet w devs only to have them lay out their approach to this the phases and tasks involved tasks schedule workshop prepare questions list prepare mural conduct session collect notes synthesize findings acceptance criteria findings documented | 0 |
325,881 | 9,937,209,257 | IssuesEvent | 2019-07-02 21:13:23 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.forbes.com - design is broken | browser-fixme priority-important type-tracking-protection-basic | <!-- @browser: Mobile Safari 12.1.2 -->
<!-- @ua_header: Mozilla/5.0 (iPad; CPU OS 11_1_2 like Mac OS X; en-GB) AppleWebKit/536.13.23 (KHTML, like Gecko) Version/12.1.2 Mobile/8J390 Safari/536.13.23 -->
<!-- @reported_with: mobile-reporter -->
<!-- @extra_labels: type-tracking-protection-basic -->
**URL**: https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/#db850dc5b752
**Browser / Version**: Mobile Safari 12.1.2
**Operating System**: iOS 11.1.2
**Tested Another Browser**: No
**Problem type**: Design is broken
**Description**: can't read text
**Steps to Reproduce**:
[](https://webcompat.com/uploads/2019/7/52aad1f5-e948-4321-9b6b-58de1eeeb934.jpeg)
<details>
<summary>Browser Configuration</summary>
<ul>
<li>mixed active content blocked: false</li><li>image.mem.shared: true</li><li>buildID: 20190628222626</li><li>tracking content blocked: true (basic)</li><li>gfx.webrender.blob-images: true</li><li>hasTouchScreen: true</li><li>mixed passive content blocked: false</li><li>gfx.webrender.enabled: false</li><li>gfx.webrender.all: false</li><li>channel: nightly</li>
</ul>
<p>Console Messages:</p>
<pre>
[u'[JavaScript Warning: "The resource at https://www.googletagservices.com/tag/js/gpt.js was blocked because content blocking is enabled." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 0}]', u'[JavaScript Warning: "The resource at https://native.sharethrough.com/assets/sfp.js was blocked because content blocking is enabled." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 0}]', u'[JavaScript Warning: "downloadable font: no supported format found (font-family: "forbesicon" style:normal weight:400 stretch:100 src index:1) source: (end of source list)" {file: "unknown" line: 1 column: 33594 source: "@font-face {\n font-family: "forbesicon";\n src: url("https://i.forbesimg.com/assets/fonts/fbs-typography/0233/forbesicon.svg#forbesicon") format("svg");\n}"}]', u'[JavaScript Warning: "Loading failed for the <script> with source https://native.sharethrough.com/assets/sfp.js." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 2}]', u'[JavaScript Warning: "Loading failed for the <script> with source https://cdn.speedcurve.com/js/lux.js?id=22432108." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 2}]', u'[JavaScript Warning: "The resource at https://contextual.media.net/bidexchange.js?cid=8CUX956JU&https=1 was blocked because content blocking is enabled." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 0}]', u'[JavaScript Warning: "The resource at https://static.criteo.net/js/ld/publishertag.js was blocked because content blocking is enabled." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 0}]', u'[JavaScript Warning: "The resource at https://c.amazon-adsystem.com/aax2/apstag.js was blocked because content blocking is enabled." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 0}]', u'[JavaScript Warning: "The resource at https://z.moatads.com/forbesprebidheader122641196143/yi.js was blocked because content blocking is enabled." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 0}]', u'[JavaScript Warning: "The resource at https://www.googletagservices.com/tag/js/gpt.js was blocked because content blocking is enabled." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 0}]', u'[JavaScript Warning: "Loading failed for the <script> with source https://contextual.media.net/bidexchange.js?cid=8CUX956JU&https=1." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 1}]', u'[JavaScript Warning: "Loading failed for the <script> with source https://static.criteo.net/js/ld/publishertag.js." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 1}]', u'[JavaScript Warning: "Loading failed for the <script> with source https://c.amazon-adsystem.com/aax2/apstag.js." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 1}]', u'[JavaScript Warning: "Loading failed for the <script> with source https://z.moatads.com/forbesprebidheader122641196143/yi.js." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 1}]', u'[console.time(GET: /forbesapi/stats/topStories.json?channel=channel_3&objects=true&mobile=false&fields=primaryChannelId,storyType,blogType,advoiceBrand,shortUri,title,date,naturalId,authors,image,uri,slug&naturalid=blogAndPostId/blog/post/1927-3613&stream=true&specialslot=&swimlane=undefined&limit=10&bvleftrail=true&blogid=1927&brandvoice=false&insights=false) https://i.forbesimg.com/ng2/ddfd33af4ef2acbb0754.app.js:1:65511]', u'[JavaScript Warning: "downloadable font: no supported format found (font-family: "forbesicon" style:normal weight:400 stretch:100 src index:1) source: (end of source list)" {file: "unknown" line: 1 column: 33594 source: "@font-face {\n font-family: "forbesicon";\n src: url("https://i.forbesimg.com/assets/fonts/fbs-typography/0233/forbesicon.svg#forbesicon") format("svg");\n}"}]', u'[console.time(GET: /statsapi/page/all/20/id.json2?id=blogAndPostId/blog/post/1927-3613) https://i.forbesimg.com/ng2/ddfd33af4ef2acbb0754.app.js:1:65511]', u'[console.error(Error targeting MOAT yield for slot, ) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:349237]', u'[JavaScript Warning: "The resource at https://contextual.media.net/dmedianet.js?cid=8CU2T3HV4&https=1 was blocked because content blocking is enabled." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/#db850dc5b752" line: 0}]', u'[console.error(Error targeting MOAT yield for slot, ) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:349237]', u'[console.error(Error targeting MOAT yield for slot, ) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:349237]', u'[console.error(TypeError: n.criteo is undefined) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:351213]', u'[console.error(Error targeting MOAT yield for slot, ) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:349237]', u'[console.error(TypeError: n.criteo is undefined) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:351213]', u'[console.error(Error targeting MOAT yield for slot, ) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:349237]', u'[console.error(Error targeting MOAT yield for slot, ) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:349237]', u'[console.error(TypeError: n.criteo is undefined) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:351213]', u'[JavaScript Warning: "The resource at https://adservex.media.net/videoAds.js?cid=8CU2Y65FS&crid=545004763&https=1&dn=forbes.com was blocked because content blocking is enabled." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/#db850dc5b752" line: 0}]', u'[JavaScript Warning: "Loading failed for the <script> with source https://contextual.media.net/dmedianet.js?cid=8CU2T3HV4&https=1." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/#db850dc5b752" line: 1}]', u'[JavaScript Warning: "Loading failed for the <script> with source https://adservex.media.net/videoAds.js?cid=8CU2Y65FS&crid=545004763&https=1&dn=forbes.com." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/#db850dc5b752" line: 1}]', u'[console.timeEnd(GET: /forbesapi/stats/topStories.json?channel=channel_3&objects=true&mobile=false&fields=primaryChannelId,storyType,blogType,advoiceBrand,shortUri,title,date,naturalId,authors,image,uri,slug&naturalid=blogAndPostId/blog/post/1927-3613&stream=true&specialslot=&swimlane=undefined&limit=10&bvleftrail=true&blogid=1927&brandvoice=false&insights=false) https://i.forbesimg.com/ng2/ddfd33af4ef2acbb0754.app.js:1:65600]', u'[console.timeEnd(GET: /statsapi/page/all/20/id.json2?id=blogAndPostId/blog/post/1927-3613) https://i.forbesimg.com/ng2/ddfd33af4ef2acbb0754.app.js:1:65600]', u'[console.error(Error targeting MOAT yield for slot, ) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:349237]', u'[console.error(Error targeting MOAT yield for slot, ) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:349237]', u'[console.error(Error targeting MOAT yield for slot, ) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:349237]']
</pre>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | www.forbes.com - design is broken - <!-- @browser: Mobile Safari 12.1.2 -->
<!-- @ua_header: Mozilla/5.0 (iPad; CPU OS 11_1_2 like Mac OS X; en-GB) AppleWebKit/536.13.23 (KHTML, like Gecko) Version/12.1.2 Mobile/8J390 Safari/536.13.23 -->
<!-- @reported_with: mobile-reporter -->
<!-- @extra_labels: type-tracking-protection-basic -->
**URL**: https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/#db850dc5b752
**Browser / Version**: Mobile Safari 12.1.2
**Operating System**: iOS 11.1.2
**Tested Another Browser**: No
**Problem type**: Design is broken
**Description**: can't read text
**Steps to Reproduce**:
[](https://webcompat.com/uploads/2019/7/52aad1f5-e948-4321-9b6b-58de1eeeb934.jpeg)
<details>
<summary>Browser Configuration</summary>
<ul>
<li>mixed active content blocked: false</li><li>image.mem.shared: true</li><li>buildID: 20190628222626</li><li>tracking content blocked: true (basic)</li><li>gfx.webrender.blob-images: true</li><li>hasTouchScreen: true</li><li>mixed passive content blocked: false</li><li>gfx.webrender.enabled: false</li><li>gfx.webrender.all: false</li><li>channel: nightly</li>
</ul>
<p>Console Messages:</p>
<pre>
[u'[JavaScript Warning: "The resource at https://www.googletagservices.com/tag/js/gpt.js was blocked because content blocking is enabled." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 0}]', u'[JavaScript Warning: "The resource at https://native.sharethrough.com/assets/sfp.js was blocked because content blocking is enabled." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 0}]', u'[JavaScript Warning: "downloadable font: no supported format found (font-family: "forbesicon" style:normal weight:400 stretch:100 src index:1) source: (end of source list)" {file: "unknown" line: 1 column: 33594 source: "@font-face {\n font-family: "forbesicon";\n src: url("https://i.forbesimg.com/assets/fonts/fbs-typography/0233/forbesicon.svg#forbesicon") format("svg");\n}"}]', u'[JavaScript Warning: "Loading failed for the <script> with source https://native.sharethrough.com/assets/sfp.js." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 2}]', u'[JavaScript Warning: "Loading failed for the <script> with source https://cdn.speedcurve.com/js/lux.js?id=22432108." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 2}]', u'[JavaScript Warning: "The resource at https://contextual.media.net/bidexchange.js?cid=8CUX956JU&https=1 was blocked because content blocking is enabled." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 0}]', u'[JavaScript Warning: "The resource at https://static.criteo.net/js/ld/publishertag.js was blocked because content blocking is enabled." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 0}]', u'[JavaScript Warning: "The resource at https://c.amazon-adsystem.com/aax2/apstag.js was blocked because content blocking is enabled." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 0}]', u'[JavaScript Warning: "The resource at https://z.moatads.com/forbesprebidheader122641196143/yi.js was blocked because content blocking is enabled." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 0}]', u'[JavaScript Warning: "The resource at https://www.googletagservices.com/tag/js/gpt.js was blocked because content blocking is enabled." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 0}]', u'[JavaScript Warning: "Loading failed for the <script> with source https://contextual.media.net/bidexchange.js?cid=8CUX956JU&https=1." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 1}]', u'[JavaScript Warning: "Loading failed for the <script> with source https://static.criteo.net/js/ld/publishertag.js." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 1}]', u'[JavaScript Warning: "Loading failed for the <script> with source https://c.amazon-adsystem.com/aax2/apstag.js." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 1}]', u'[JavaScript Warning: "Loading failed for the <script> with source https://z.moatads.com/forbesprebidheader122641196143/yi.js." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/" line: 1}]', u'[console.time(GET: /forbesapi/stats/topStories.json?channel=channel_3&objects=true&mobile=false&fields=primaryChannelId,storyType,blogType,advoiceBrand,shortUri,title,date,naturalId,authors,image,uri,slug&naturalid=blogAndPostId/blog/post/1927-3613&stream=true&specialslot=&swimlane=undefined&limit=10&bvleftrail=true&blogid=1927&brandvoice=false&insights=false) https://i.forbesimg.com/ng2/ddfd33af4ef2acbb0754.app.js:1:65511]', u'[JavaScript Warning: "downloadable font: no supported format found (font-family: "forbesicon" style:normal weight:400 stretch:100 src index:1) source: (end of source list)" {file: "unknown" line: 1 column: 33594 source: "@font-face {\n font-family: "forbesicon";\n src: url("https://i.forbesimg.com/assets/fonts/fbs-typography/0233/forbesicon.svg#forbesicon") format("svg");\n}"}]', u'[console.time(GET: /statsapi/page/all/20/id.json2?id=blogAndPostId/blog/post/1927-3613) https://i.forbesimg.com/ng2/ddfd33af4ef2acbb0754.app.js:1:65511]', u'[console.error(Error targeting MOAT yield for slot, ) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:349237]', u'[JavaScript Warning: "The resource at https://contextual.media.net/dmedianet.js?cid=8CU2T3HV4&https=1 was blocked because content blocking is enabled." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/#db850dc5b752" line: 0}]', u'[console.error(Error targeting MOAT yield for slot, ) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:349237]', u'[console.error(Error targeting MOAT yield for slot, ) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:349237]', u'[console.error(TypeError: n.criteo is undefined) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:351213]', u'[console.error(Error targeting MOAT yield for slot, ) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:349237]', u'[console.error(TypeError: n.criteo is undefined) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:351213]', u'[console.error(Error targeting MOAT yield for slot, ) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:349237]', u'[console.error(Error targeting MOAT yield for slot, ) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:349237]', u'[console.error(TypeError: n.criteo is undefined) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:351213]', u'[JavaScript Warning: "The resource at https://adservex.media.net/videoAds.js?cid=8CU2Y65FS&crid=545004763&https=1&dn=forbes.com was blocked because content blocking is enabled." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/#db850dc5b752" line: 0}]', u'[JavaScript Warning: "Loading failed for the <script> with source https://contextual.media.net/dmedianet.js?cid=8CU2T3HV4&https=1." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/#db850dc5b752" line: 1}]', u'[JavaScript Warning: "Loading failed for the <script> with source https://adservex.media.net/videoAds.js?cid=8CU2Y65FS&crid=545004763&https=1&dn=forbes.com." {file: "https://www.forbes.com/sites/eliseackerman/2014/12/16/qualcomms-new-snapdragon-810-versus-apples-a8-the-chipset-behind-the-iphone-6-and-6-plus/#db850dc5b752" line: 1}]', u'[console.timeEnd(GET: /forbesapi/stats/topStories.json?channel=channel_3&objects=true&mobile=false&fields=primaryChannelId,storyType,blogType,advoiceBrand,shortUri,title,date,naturalId,authors,image,uri,slug&naturalid=blogAndPostId/blog/post/1927-3613&stream=true&specialslot=&swimlane=undefined&limit=10&bvleftrail=true&blogid=1927&brandvoice=false&insights=false) https://i.forbesimg.com/ng2/ddfd33af4ef2acbb0754.app.js:1:65600]', u'[console.timeEnd(GET: /statsapi/page/all/20/id.json2?id=blogAndPostId/blog/post/1927-3613) https://i.forbesimg.com/ng2/ddfd33af4ef2acbb0754.app.js:1:65600]', u'[console.error(Error targeting MOAT yield for slot, ) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:349237]', u'[console.error(Error targeting MOAT yield for slot, ) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:349237]', u'[console.error(Error targeting MOAT yield for slot, ) https://i.forbesimg.com/ng2/859f4ca8240b22c0b6c0.vendors.js:1:349237]']
</pre>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_ | non_defect | design is broken url browser version mobile safari operating system ios tested another browser no problem type design is broken description can t read text steps to reproduce browser configuration mixed active content blocked false image mem shared true buildid tracking content blocked true basic gfx webrender blob images true hastouchscreen true mixed passive content blocked false gfx webrender enabled false gfx webrender all false channel nightly console messages u u u u u u u u u u u u u u u u u u u u u u u u u u u u u u u u u u from with ❤️ | 0 |
107,246 | 4,295,677,542 | IssuesEvent | 2016-07-19 08:12:30 | flipdazed/Hybrid-Monte-Carlo | https://api.github.com/repos/flipdazed/Hybrid-Monte-Carlo | closed | Errors for Autocorrelations & Mixing with uWerr tests | Enhancement High Priority Top of List | **Issue**
There are two series of plots:
- `acorr1d_xx`
- `errs`
Since `errs` is the most recent and contains errors on autocorrelations this has become the main routine. This should be reserved as a test of `uWerr` rather than a self-contained autocorrelation plot.
**Resolution**
- Introduce error bars into `acorr1d`
- `errors_xx_khmc_kg` is misleading as it is actually just a multiple plot of `errs_xx_hmc_kg`
- Rename `errors_xx_khmc_kg` to make it clear that this is actually testing the windowing | 1.0 | Errors for Autocorrelations & Mixing with uWerr tests - **Issue**
There are two series of plots:
- `acorr1d_xx`
- `errs`
Since `errs` is the most recent and contains errors on autocorrelations this has become the main routine. This should be reserved as a test of `uWerr` rather than a self-contained autocorrelation plot.
**Resolution**
- Introduce error bars into `acorr1d`
- `errors_xx_khmc_kg` is misleading as it is actually just a multiple plot of `errs_xx_hmc_kg`
- Rename `errors_xx_khmc_kg` to make it clear that this is actually testing the windowing | non_defect | errors for autocorrelations mixing with uwerr tests issue there are two series of plots xx errs since errs is the most recent and contains errors on autocorrelations this has become the main routine this should be reserved as a test of uwerr rather than a self contained autocorrelation plot resolution introduce error bars into errors xx khmc kg is misleading as it is actually just a multiple plot of errs xx hmc kg rename errors xx khmc kg to make it clear that this is actually testing the windowing | 0 |
7,991 | 2,611,071,391 | IssuesEvent | 2015-02-27 00:33:20 | alistairreilly/andors-trail | https://api.github.com/repos/alistairreilly/andors-trail | opened | Loot popup display | auto-migrated Priority-Low Type-Defect | ```
Reported by PK17 on the forums:
When you kill an enemy who drops an item. If you immediately (very very
quickly) touch the area between the item(s) dropped and the "pick up all" and
"exit" options (right in between them) a small sliver (about the size of a
listed item) of the loot dialog box become semi-transparent and the map can be
seen through the box.
When the items show up in the box you touch and hold, the item will then be
highlighted (mine is blue) then slide your finger away from the item then
release your touch. You should then see these results replicated. If not it
might be my phone.
http://andorstrail.com/viewtopic.php?f=3&t=3332
```
Original issue reported on code.google.com by `oskar.wi...@gmail.com` on 21 Apr 2013 at 4:51
Attachments:
* [724.png](https://storage.googleapis.com/google-code-attachments/andors-trail/issue-341/comment-0/724.png)
| 1.0 | Loot popup display - ```
Reported by PK17 on the forums:
When you kill an enemy who drops an item. If you immediately (very very
quickly) touch the area between the item(s) dropped and the "pick up all" and
"exit" options (right in between them) a small sliver (about the size of a
listed item) of the loot dialog box become semi-transparent and the map can be
seen through the box.
When the items show up in the box you touch and hold, the item will then be
highlighted (mine is blue) then slide your finger away from the item then
release your touch. You should then see these results replicated. If not it
might be my phone.
http://andorstrail.com/viewtopic.php?f=3&t=3332
```
Original issue reported on code.google.com by `oskar.wi...@gmail.com` on 21 Apr 2013 at 4:51
Attachments:
* [724.png](https://storage.googleapis.com/google-code-attachments/andors-trail/issue-341/comment-0/724.png)
| defect | loot popup display reported by on the forums when you kill an enemy who drops an item if you immediately very very quickly touch the area between the item s dropped and the pick up all and exit options right in between them a small sliver about the size of a listed item of the loot dialog box become semi transparent and the map can be seen through the box when the items show up in the box you touch and hold the item will then be highlighted mine is blue then slide your finger away from the item then release your touch you should then see these results replicated if not it might be my phone original issue reported on code google com by oskar wi gmail com on apr at attachments | 1 |
73,273 | 24,535,715,230 | IssuesEvent | 2022-10-11 20:32:42 | zed-industries/feedback | https://api.github.com/repos/zed-industries/feedback | opened | Don't disable .gitignore'd files defined beyond the first parent directory that contains a git repository | defect triage | ### Check for existing issues
- [X] Completed
### Describe the bug / provide steps to reproduce it
I set up my home directory as a git repository to sync my shell config between machines. I have a .gitignore there which includes my code projects (separate git repos). After setting this up, I noticed that any repo I open Zed has every file greyed out in the sidebar as if it was .gitignore'd.
Steps to reproduce:
1. Create a git repository in the home directory with a .gitignore file
```sh
cd ~
git init
echo "*.txt" > .gitignore
```
2. Create a git repo with a single file in the home directory
```sh
mkdir example-repo
cd example-repo
git init
touch example.txt
```
3. Open the repo in Zed
```
zed .
```
I suspect this was introduced with the fix for #85
### Expected behavior
I expect `example.txt` file to be available in the sidebar. Instead it is greyed out even though it is not included in the project's .gitignore (but is in the parent directory's).
This also means I can't use `Cmd+P` to open file patterns ignored in the parent git repository but not the project git repository.
### Environment
Zed 0.59.0 – /Applications/Zed.app
macOS 12.6
architecture x86_64
### If applicable, add mockups / screenshots to help explain present your vision of the feature
_No response_
### If applicable, attach your `~/Library/Logs/Zed/Zed.log` file to this issue
_No response_ | 1.0 | Don't disable .gitignore'd files defined beyond the first parent directory that contains a git repository - ### Check for existing issues
- [X] Completed
### Describe the bug / provide steps to reproduce it
I set up my home directory as a git repository to sync my shell config between machines. I have a .gitignore there which includes my code projects (separate git repos). After setting this up, I noticed that any repo I open Zed has every file greyed out in the sidebar as if it was .gitignore'd.
Steps to reproduce:
1. Create a git repository in the home directory with a .gitignore file
```sh
cd ~
git init
echo "*.txt" > .gitignore
```
2. Create a git repo with a single file in the home directory
```sh
mkdir example-repo
cd example-repo
git init
touch example.txt
```
3. Open the repo in Zed
```
zed .
```
I suspect this was introduced with the fix for #85
### Expected behavior
I expect `example.txt` file to be available in the sidebar. Instead it is greyed out even though it is not included in the project's .gitignore (but is in the parent directory's).
This also means I can't use `Cmd+P` to open file patterns ignored in the parent git repository but not the project git repository.
### Environment
Zed 0.59.0 – /Applications/Zed.app
macOS 12.6
architecture x86_64
### If applicable, add mockups / screenshots to help explain present your vision of the feature
_No response_
### If applicable, attach your `~/Library/Logs/Zed/Zed.log` file to this issue
_No response_ | defect | don t disable gitignore d files defined beyond the first parent directory that contains a git repository check for existing issues completed describe the bug provide steps to reproduce it i set up my home directory as a git repository to sync my shell config between machines i have a gitignore there which includes my code projects separate git repos after setting this up i noticed that any repo i open zed has every file greyed out in the sidebar as if it was gitignore d steps to reproduce create a git repository in the home directory with a gitignore file sh cd git init echo txt gitignore create a git repo with a single file in the home directory sh mkdir example repo cd example repo git init touch example txt open the repo in zed zed i suspect this was introduced with the fix for expected behavior i expect example txt file to be available in the sidebar instead it is greyed out even though it is not included in the project s gitignore but is in the parent directory s this also means i can t use cmd p to open file patterns ignored in the parent git repository but not the project git repository environment zed – applications zed app macos architecture if applicable add mockups screenshots to help explain present your vision of the feature no response if applicable attach your library logs zed zed log file to this issue no response | 1 |
47,102 | 5,848,330,652 | IssuesEvent | 2017-05-10 20:38:44 | bounswe/bounswe2017group3 | https://api.github.com/repos/bounswe/bounswe2017group3 | closed | Create a test case for sending invitation to a user. | status: in progress testing wiki | ## About
* **Related Issues:** #85
* **Other Related Links:** [Wiki Use Cases Page](https://github.com/bounswe/bounswe2017group3/wiki/Use-Cases)
I assigned myself to complete the test case for sending invitation to a user.
## To-do
- [ ] Create a test case for sending invitation to a user.
| 1.0 | Create a test case for sending invitation to a user. - ## About
* **Related Issues:** #85
* **Other Related Links:** [Wiki Use Cases Page](https://github.com/bounswe/bounswe2017group3/wiki/Use-Cases)
I assigned myself to complete the test case for sending invitation to a user.
## To-do
- [ ] Create a test case for sending invitation to a user.
| non_defect | create a test case for sending invitation to a user about related issues other related links i assigned myself to complete the test case for sending invitation to a user to do create a test case for sending invitation to a user | 0 |
13,849 | 2,788,714,467 | IssuesEvent | 2015-05-08 15:11:29 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | closed | New Client GetAsync Fails with a NegativeArraySizeException | Team: Client Type: Defect | ```
Hazelcast.newHazelcastInstance();
IMap map = client.getMap("map");
int size = 100;
for (int i = 0; i < size; i++) {
map.put(i, i);
}
for (int i = 0; i < size; i++) {
Future f = map.getAsync(i);
f.get();
}
``` | 1.0 | New Client GetAsync Fails with a NegativeArraySizeException - ```
Hazelcast.newHazelcastInstance();
IMap map = client.getMap("map");
int size = 100;
for (int i = 0; i < size; i++) {
map.put(i, i);
}
for (int i = 0; i < size; i++) {
Future f = map.getAsync(i);
f.get();
}
``` | defect | new client getasync fails with a negativearraysizeexception hazelcast newhazelcastinstance imap map client getmap map int size for int i i size i map put i i for int i i size i future f map getasync i f get | 1 |
245,747 | 20,795,406,123 | IssuesEvent | 2022-03-17 08:48:21 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | roachtest: disk-stalled/log=true,data=true failed | C-test-failure O-robot O-roachtest release-blocker branch-release-21.2 | roachtest.disk-stalled/log=true,data=true [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=4594078&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=4594078&tab=artifacts#/disk-stalled/log=true,data=true) on release-21.2 @ [469fee64184a83b3a3afef3ed12dafa7d5d29df3](https://github.com/cockroachdb/cockroach/commits/469fee64184a83b3a3afef3ed12dafa7d5d29df3):
```
| Setting up libboost-stacktrace-dev:amd64 (1.71.0.0ubuntu2) ...
| Setting up libboost-type-erasure1.71-dev:amd64 (1.71.0-6ubuntu6) ...
| Setting up libboost-log1.71-dev (1.71.0-6ubuntu6) ...
| Setting up libboost-coroutine1.71-dev:amd64 (1.71.0-6ubuntu6) ...
| Setting up libboost-graph-parallel1.71.0 (1.71.0-6ubuntu6) ...
| Setting up libboost-coroutine-dev:amd64 (1.71.0.0ubuntu2) ...
| Setting up libboost-log-dev (1.71.0.0ubuntu2) ...
| Setting up libboost-timer-dev:amd64 (1.71.0.0ubuntu2) ...
| Setting up openmpi-bin (4.0.3-0ubuntu1) ...
| update-alternatives: using /usr/bin/mpirun.openmpi to provide /usr/bin/mpirun (mpirun) in auto mode
| update-alternatives: using /usr/bin/mpicc.openmpi to provide /usr/bin/mpicc (mpi) in auto mode
| Setting up libboost-thread-dev:amd64 (1.71.0.0ubuntu2) ...
| Setting up libboost-fiber-dev:amd64 (1.71.0.0ubuntu2) ...
| Setting up libboost-locale1.71-dev:amd64 (1.71.0-6ubuntu6) ...
| Setting up libcoarrays-dev:amd64 (2.8.0-1) ...
| Setting up libboost-python1.71-dev (1.71.0-6ubuntu6) ...
| Setting up mpi-default-bin (1.13) ...
| Setting up libboost-locale-dev:amd64 (1.71.0.0ubuntu2) ...
| Setting up libcoarrays-openmpi-dev:amd64 (2.8.0-1) ...
| Setting up libboost-python-dev (1.71.0.0ubuntu2) ...
| Setting up libboost-type-erasure-dev:amd64 (1.71.0.0ubuntu2) ...
| Setting up libboost-graph-parallel1.71-dev (1.71.0-6ubuntu6) ...
| Setting up libopenmpi-dev:amd64 (4.0.3-0ubuntu1) ...
| update-alternatives: using /usr/lib/x86_64-linux-gnu/openmpi/include to provide /usr/include/x86_64-linux-gnu/mpi (mpi-x86_64-linux-gnu) in auto mode
| Setting up libboost-mpi-python1.71.0 (1.71.0-6ubuntu6) ...
| Setting up libboost-graph-parallel-dev (1.71.0.0ubuntu2) ...
| Setting up mpi-default-dev (1.13) ...
| Setting up libboost-mpi1.71-dev (1.71.0-6ubuntu6) ...
| Setting up libboost-mpi-python1.71-dev (1.71.0-6ubuntu6) ...
| Setting up libboost-mpi-python-dev (1.71.0.0ubuntu2) ...
| Setting up libboost-mpi-dev (1.71.0.0ubuntu2) ...
| Setting up libboost-all-dev (1.71.0.0ubuntu2) ...
| Processing triggers for mime-support (3.64ubuntu1) ...
| Processing triggers for libc-bin (2.31-0ubuntu9.2) ...
| Processing triggers for man-db (2.9.1-1) ...
| Processing triggers for install-info (6.7.0.dfsg.2-5) ...
| + sudo mkdir -p /opt/thrift
| + sudo chmod 777 /opt/thrift
| + cd /opt/thrift
| + curl https://downloads.apache.org/thrift/0.13.0/thrift-0.13.0.tar.gz
| + sudo tar xvz --strip-components 1
| % Total % Received % Xferd Average Speed Time Time Time Current
| Dload Upload Total Spent Left Speed
|
0 0 0 0 0 0 0 0 --:--:-- --:--:-- --:--:-- 0
100 196 100 196 0 0 525 0 --:--:-- --:--:-- --:--:-- 525
100 196 100 196 0 0 525 0 --:--:-- --:--:-- --:--:-- 524
|
| gzip: stdin: not in gzip format
| tar: Child returned status 1
| tar: Error is not recoverable: exiting now
Wraps: (2) exit status 20
Error types: (1) *cluster.WithCommandDetails (2) *exec.ExitError
```
<details><summary>Reproduce</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
</p>
</details>
<details><summary>Same failure on other branches</summary>
<p>
- #78008 roachtest: disk-stalled/log=true,data=true failed [C-test-failure O-roachtest O-robot T-storage branch-master release-blocker]
- #63950 roachtest: disk-stalled/log=true,data=true failed [C-test-failure O-roachtest O-robot T-storage branch-release-21.1]
- #57601 roachtest: disk-stalled/log=true,data=true failed [C-test-failure O-roachtest O-robot T-storage branch-release-20.2]
</p>
</details>
/cc @cockroachdb/storage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*disk-stalled/log=true,data=true.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 2.0 | roachtest: disk-stalled/log=true,data=true failed - roachtest.disk-stalled/log=true,data=true [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=4594078&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=4594078&tab=artifacts#/disk-stalled/log=true,data=true) on release-21.2 @ [469fee64184a83b3a3afef3ed12dafa7d5d29df3](https://github.com/cockroachdb/cockroach/commits/469fee64184a83b3a3afef3ed12dafa7d5d29df3):
```
| Setting up libboost-stacktrace-dev:amd64 (1.71.0.0ubuntu2) ...
| Setting up libboost-type-erasure1.71-dev:amd64 (1.71.0-6ubuntu6) ...
| Setting up libboost-log1.71-dev (1.71.0-6ubuntu6) ...
| Setting up libboost-coroutine1.71-dev:amd64 (1.71.0-6ubuntu6) ...
| Setting up libboost-graph-parallel1.71.0 (1.71.0-6ubuntu6) ...
| Setting up libboost-coroutine-dev:amd64 (1.71.0.0ubuntu2) ...
| Setting up libboost-log-dev (1.71.0.0ubuntu2) ...
| Setting up libboost-timer-dev:amd64 (1.71.0.0ubuntu2) ...
| Setting up openmpi-bin (4.0.3-0ubuntu1) ...
| update-alternatives: using /usr/bin/mpirun.openmpi to provide /usr/bin/mpirun (mpirun) in auto mode
| update-alternatives: using /usr/bin/mpicc.openmpi to provide /usr/bin/mpicc (mpi) in auto mode
| Setting up libboost-thread-dev:amd64 (1.71.0.0ubuntu2) ...
| Setting up libboost-fiber-dev:amd64 (1.71.0.0ubuntu2) ...
| Setting up libboost-locale1.71-dev:amd64 (1.71.0-6ubuntu6) ...
| Setting up libcoarrays-dev:amd64 (2.8.0-1) ...
| Setting up libboost-python1.71-dev (1.71.0-6ubuntu6) ...
| Setting up mpi-default-bin (1.13) ...
| Setting up libboost-locale-dev:amd64 (1.71.0.0ubuntu2) ...
| Setting up libcoarrays-openmpi-dev:amd64 (2.8.0-1) ...
| Setting up libboost-python-dev (1.71.0.0ubuntu2) ...
| Setting up libboost-type-erasure-dev:amd64 (1.71.0.0ubuntu2) ...
| Setting up libboost-graph-parallel1.71-dev (1.71.0-6ubuntu6) ...
| Setting up libopenmpi-dev:amd64 (4.0.3-0ubuntu1) ...
| update-alternatives: using /usr/lib/x86_64-linux-gnu/openmpi/include to provide /usr/include/x86_64-linux-gnu/mpi (mpi-x86_64-linux-gnu) in auto mode
| Setting up libboost-mpi-python1.71.0 (1.71.0-6ubuntu6) ...
| Setting up libboost-graph-parallel-dev (1.71.0.0ubuntu2) ...
| Setting up mpi-default-dev (1.13) ...
| Setting up libboost-mpi1.71-dev (1.71.0-6ubuntu6) ...
| Setting up libboost-mpi-python1.71-dev (1.71.0-6ubuntu6) ...
| Setting up libboost-mpi-python-dev (1.71.0.0ubuntu2) ...
| Setting up libboost-mpi-dev (1.71.0.0ubuntu2) ...
| Setting up libboost-all-dev (1.71.0.0ubuntu2) ...
| Processing triggers for mime-support (3.64ubuntu1) ...
| Processing triggers for libc-bin (2.31-0ubuntu9.2) ...
| Processing triggers for man-db (2.9.1-1) ...
| Processing triggers for install-info (6.7.0.dfsg.2-5) ...
| + sudo mkdir -p /opt/thrift
| + sudo chmod 777 /opt/thrift
| + cd /opt/thrift
| + curl https://downloads.apache.org/thrift/0.13.0/thrift-0.13.0.tar.gz
| + sudo tar xvz --strip-components 1
| % Total % Received % Xferd Average Speed Time Time Time Current
| Dload Upload Total Spent Left Speed
|
0 0 0 0 0 0 0 0 --:--:-- --:--:-- --:--:-- 0
100 196 100 196 0 0 525 0 --:--:-- --:--:-- --:--:-- 525
100 196 100 196 0 0 525 0 --:--:-- --:--:-- --:--:-- 524
|
| gzip: stdin: not in gzip format
| tar: Child returned status 1
| tar: Error is not recoverable: exiting now
Wraps: (2) exit status 20
Error types: (1) *cluster.WithCommandDetails (2) *exec.ExitError
```
<details><summary>Reproduce</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
</p>
</details>
<details><summary>Same failure on other branches</summary>
<p>
- #78008 roachtest: disk-stalled/log=true,data=true failed [C-test-failure O-roachtest O-robot T-storage branch-master release-blocker]
- #63950 roachtest: disk-stalled/log=true,data=true failed [C-test-failure O-roachtest O-robot T-storage branch-release-21.1]
- #57601 roachtest: disk-stalled/log=true,data=true failed [C-test-failure O-roachtest O-robot T-storage branch-release-20.2]
</p>
</details>
/cc @cockroachdb/storage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*disk-stalled/log=true,data=true.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| non_defect | roachtest disk stalled log true data true failed roachtest disk stalled log true data true with on release setting up libboost stacktrace dev setting up libboost type dev setting up libboost dev setting up libboost dev setting up libboost graph setting up libboost coroutine dev setting up libboost log dev setting up libboost timer dev setting up openmpi bin update alternatives using usr bin mpirun openmpi to provide usr bin mpirun mpirun in auto mode update alternatives using usr bin mpicc openmpi to provide usr bin mpicc mpi in auto mode setting up libboost thread dev setting up libboost fiber dev setting up libboost dev setting up libcoarrays dev setting up libboost dev setting up mpi default bin setting up libboost locale dev setting up libcoarrays openmpi dev setting up libboost python dev setting up libboost type erasure dev setting up libboost graph dev setting up libopenmpi dev update alternatives using usr lib linux gnu openmpi include to provide usr include linux gnu mpi mpi linux gnu in auto mode setting up libboost mpi setting up libboost graph parallel dev setting up mpi default dev setting up libboost dev setting up libboost mpi dev setting up libboost mpi python dev setting up libboost mpi dev setting up libboost all dev processing triggers for mime support processing triggers for libc bin processing triggers for man db processing triggers for install info dfsg sudo mkdir p opt thrift sudo chmod opt thrift cd opt thrift curl sudo tar xvz strip components total received xferd average speed time time time current dload upload total spent left speed gzip stdin not in gzip format tar child returned status tar error is not recoverable exiting now wraps exit status error types cluster withcommanddetails exec exiterror reproduce see same failure on other branches roachtest disk stalled log true data true failed roachtest disk stalled log true data true failed roachtest disk stalled log true data true failed cc cockroachdb storage | 0 |
76,963 | 26,695,448,581 | IssuesEvent | 2023-01-27 09:58:05 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | WYSIWYG Composer Underline Shortcut Bug | T-Defect S-Minor O-Occasional Z-Labs A-Rich-Text-Editor | ### Steps to reproduce
1. Where are you starting? What can you see? Type text in the composer with no formatting enabled. Mac on Chrome browser.
2. What do you click? Highlight the last part of the text and underline using the shortcut 'command + U'
3. The blinking carat then moves to the start of all the text and none of the text stays highlighted
4. The text that was highlighted does get formatted
### Outcome
#### What did you expect?
I expected the blinking carat to stay in the same location, the highlighted text to remain and the text to become underlined
#### What happened instead?
The text that was highlighted does get formatted, but the blinking carat moves to the start of all the text and none of the text stays highlighted
### Operating system
macOS
### Browser information
Chrome Version 106.0.5249.119 (Official Build) (arm64)
### URL for webapp
develop.element.io
### Application version
_No response_
### Homeserver
matrix.org
### Will you send logs?
No | 1.0 | WYSIWYG Composer Underline Shortcut Bug - ### Steps to reproduce
1. Where are you starting? What can you see? Type text in the composer with no formatting enabled. Mac on Chrome browser.
2. What do you click? Highlight the last part of the text and underline using the shortcut 'command + U'
3. The blinking carat then moves to the start of all the text and none of the text stays highlighted
4. The text that was highlighted does get formatted
### Outcome
#### What did you expect?
I expected the blinking carat to stay in the same location, the highlighted text to remain and the text to become underlined
#### What happened instead?
The text that was highlighted does get formatted, but the blinking carat moves to the start of all the text and none of the text stays highlighted
### Operating system
macOS
### Browser information
Chrome Version 106.0.5249.119 (Official Build) (arm64)
### URL for webapp
develop.element.io
### Application version
_No response_
### Homeserver
matrix.org
### Will you send logs?
No | defect | wysiwyg composer underline shortcut bug steps to reproduce where are you starting what can you see type text in the composer with no formatting enabled mac on chrome browser what do you click highlight the last part of the text and underline using the shortcut command u the blinking carat then moves to the start of all the text and none of the text stays highlighted the text that was highlighted does get formatted outcome what did you expect i expected the blinking carat to stay in the same location the highlighted text to remain and the text to become underlined what happened instead the text that was highlighted does get formatted but the blinking carat moves to the start of all the text and none of the text stays highlighted operating system macos browser information chrome version official build url for webapp develop element io application version no response homeserver matrix org will you send logs no | 1 |
11,652 | 9,337,018,968 | IssuesEvent | 2019-03-28 23:13:06 | aspnet/AspNetCore | https://api.github.com/repos/aspnet/AspNetCore | closed | [Helix] Tests skipped due to can't find sln | area-infrastructure test-failure | Tracking all the tests that are skipped due to depending on a sln file being present. (Src is not part of helix test payloads)
```
Azure\ApplicationInsights.HostingStartup\test\UnitTests\JavaScriptSnippetTest.cs (all tests)
Azure\ApplicationInsights.HostingStartup\test\UnitTests\LoggingTest.cs (all tests)
DefaultBuilder\test\Microsoft.AspNetCore.FunctionalTests\WebHostFunctionalTests.cs (all tests)
Hosting\test\FunctionalTests\WebHostBuilderTests.cs (all tests)
Identity\test\Identity.Test\CdnScriptTaghelperTests.cs (IdentityUI_ScriptTags_SubresourceIntegrityCheck)
mvc\test\Microsoft.AspNetCore.Mvc.Analyzers.Test\AvoidHtmlPartialAnalyzerTest.cs
\Razor\Mvc.Razor.Extensions\test\IntegrationTestsCodeGenerationIntegrationTest.cs (all tests)
```
| 1.0 | [Helix] Tests skipped due to can't find sln - Tracking all the tests that are skipped due to depending on a sln file being present. (Src is not part of helix test payloads)
```
Azure\ApplicationInsights.HostingStartup\test\UnitTests\JavaScriptSnippetTest.cs (all tests)
Azure\ApplicationInsights.HostingStartup\test\UnitTests\LoggingTest.cs (all tests)
DefaultBuilder\test\Microsoft.AspNetCore.FunctionalTests\WebHostFunctionalTests.cs (all tests)
Hosting\test\FunctionalTests\WebHostBuilderTests.cs (all tests)
Identity\test\Identity.Test\CdnScriptTaghelperTests.cs (IdentityUI_ScriptTags_SubresourceIntegrityCheck)
mvc\test\Microsoft.AspNetCore.Mvc.Analyzers.Test\AvoidHtmlPartialAnalyzerTest.cs
\Razor\Mvc.Razor.Extensions\test\IntegrationTestsCodeGenerationIntegrationTest.cs (all tests)
```
| non_defect | tests skipped due to can t find sln tracking all the tests that are skipped due to depending on a sln file being present src is not part of helix test payloads azure applicationinsights hostingstartup test unittests javascriptsnippettest cs all tests azure applicationinsights hostingstartup test unittests loggingtest cs all tests defaultbuilder test microsoft aspnetcore functionaltests webhostfunctionaltests cs all tests hosting test functionaltests webhostbuildertests cs all tests identity test identity test cdnscripttaghelpertests cs identityui scripttags subresourceintegritycheck mvc test microsoft aspnetcore mvc analyzers test avoidhtmlpartialanalyzertest cs razor mvc razor extensions test integrationtestscodegenerationintegrationtest cs all tests | 0 |
43,184 | 11,543,675,392 | IssuesEvent | 2020-02-18 10:01:56 | mozilla-lockwise/lockwise-android | https://api.github.com/repos/mozilla-lockwise/lockwise-android | opened | There is no select animation displayed for "Alphabetically" and "Recently Used" buttons on the home screen | defect | ## Steps to reproduce
1. Launch Lockwise.
2. On the home screen tap on the `All logins` button.
3. Tap and hold on the option that is not currently set.
### Expected behavior
There should be a select animation displayed while tapping and holding one of the `Alphabetically or Recently Used` buttons.
### Actual behavior
There is no select animation displayed for "Alphabetically" and "Recently Used" buttons on the home screen.
### Device & build information
* Device: Samsung Galaxy S10+ (Android 9).
* Build version: **4.0.0 (Build 6087).**
### Notes
**Note that only for the currently selected option the select animation is displayed.**
Attachments:

| 1.0 | There is no select animation displayed for "Alphabetically" and "Recently Used" buttons on the home screen - ## Steps to reproduce
1. Launch Lockwise.
2. On the home screen tap on the `All logins` button.
3. Tap and hold on the option that is not currently set.
### Expected behavior
There should be a select animation displayed while tapping and holding one of the `Alphabetically or Recently Used` buttons.
### Actual behavior
There is no select animation displayed for "Alphabetically" and "Recently Used" buttons on the home screen.
### Device & build information
* Device: Samsung Galaxy S10+ (Android 9).
* Build version: **4.0.0 (Build 6087).**
### Notes
**Note that only for the currently selected option the select animation is displayed.**
Attachments:

| defect | there is no select animation displayed for alphabetically and recently used buttons on the home screen steps to reproduce launch lockwise on the home screen tap on the all logins button tap and hold on the option that is not currently set expected behavior there should be a select animation displayed while tapping and holding one of the alphabetically or recently used buttons actual behavior there is no select animation displayed for alphabetically and recently used buttons on the home screen device build information device samsung galaxy android build version build notes note that only for the currently selected option the select animation is displayed attachments | 1 |
136,789 | 30,591,180,088 | IssuesEvent | 2023-07-21 17:12:02 | pinterest/ktlint | https://api.github.com/repos/pinterest/ktlint | closed | Add new rule to rewrite the class signature | new rule ktlint-official-codestyle class-signature rule | **EDIT:** I can workaround by avoiding writing code like this (instead let the constructor be at the same line with class name). I just want to report it so you can know that it happens, but please make this a low priority.
---
Hi thanks for the lib! For the following code, intellij idea thinks there should be 4 spaces at `(message: String?)` while ktlint thinks 0.
```
cat ~/temp/a.kt && java -jar /Users/tom/opt/ktlint-0.44.0-20220123.092956-49-all.jar ~/temp/a.kt --debug
package hello
class MyException
(message: String?) : RuntimeException(message)
[DEBUG] Discovered reporter with "baseline" id.
[DEBUG] Discovered reporter with "checkstyle" id.
[DEBUG] Discovered reporter with "json" id.
[DEBUG] Discovered reporter with "html" id.
[DEBUG] Discovered reporter with "plain" id.
[DEBUG] Discovered reporter with "sarif" id.
[DEBUG] Initializing "plain" reporter with {verbose=false, color=false, color_name=DARK_GRAY}
[DEBUG] Rule with id 'standard:max-line-length' should run after the rule with id 'experimental:trailing-comma'. However, the latter rule is not loaded and is allowed to be ignored. For best results, it is advised load the rule.
[DEBUG] Rules will be executed in order below (unless disabled):
- standard:filename,
- standard:final-newline,
- standard:chain-wrapping,
- standard:colon-spacing,
- standard:comma-spacing,
- standard:comment-spacing,
- standard:curly-spacing,
- standard:dot-spacing,
- standard:import-ordering,
- standard:keyword-spacing,
- standard:modifier-order,
- standard:no-blank-line-before-rbrace,
- standard:no-consecutive-blank-lines,
- standard:no-empty-class-body,
- standard:no-line-break-after-else,
- standard:no-line-break-before-assignment,
- standard:no-multi-spaces,
- standard:no-semi,
- standard:no-trailing-spaces,
- standard:no-unit-return,
- standard:no-unused-imports,
- standard:no-wildcard-imports,
- standard:op-spacing,
- standard:parameter-list-wrapping,
- standard:paren-spacing,
- standard:range-spacing,
- standard:string-template,
- standard:indent,
- standard:max-line-length
[DEBUG] Checking /Users/tom/temp/a.kt
Resolving .editorconfig files for /Users/tom/temp/a.kt file path
Loaded .editorconfig: []
/Users/tom/temp/a.kt:1:1: class MyException should be declared in a file named MyException.kt (cannot be auto-corrected)
/Users/tom/temp/a.kt:4:1: Unexpected indentation (4) (should be 0)
[DEBUG] 784ms / 1 file(s) / 2 error(s)
``` | 1.0 | Add new rule to rewrite the class signature - **EDIT:** I can workaround by avoiding writing code like this (instead let the constructor be at the same line with class name). I just want to report it so you can know that it happens, but please make this a low priority.
---
Hi thanks for the lib! For the following code, intellij idea thinks there should be 4 spaces at `(message: String?)` while ktlint thinks 0.
```
cat ~/temp/a.kt && java -jar /Users/tom/opt/ktlint-0.44.0-20220123.092956-49-all.jar ~/temp/a.kt --debug
package hello
class MyException
(message: String?) : RuntimeException(message)
[DEBUG] Discovered reporter with "baseline" id.
[DEBUG] Discovered reporter with "checkstyle" id.
[DEBUG] Discovered reporter with "json" id.
[DEBUG] Discovered reporter with "html" id.
[DEBUG] Discovered reporter with "plain" id.
[DEBUG] Discovered reporter with "sarif" id.
[DEBUG] Initializing "plain" reporter with {verbose=false, color=false, color_name=DARK_GRAY}
[DEBUG] Rule with id 'standard:max-line-length' should run after the rule with id 'experimental:trailing-comma'. However, the latter rule is not loaded and is allowed to be ignored. For best results, it is advised load the rule.
[DEBUG] Rules will be executed in order below (unless disabled):
- standard:filename,
- standard:final-newline,
- standard:chain-wrapping,
- standard:colon-spacing,
- standard:comma-spacing,
- standard:comment-spacing,
- standard:curly-spacing,
- standard:dot-spacing,
- standard:import-ordering,
- standard:keyword-spacing,
- standard:modifier-order,
- standard:no-blank-line-before-rbrace,
- standard:no-consecutive-blank-lines,
- standard:no-empty-class-body,
- standard:no-line-break-after-else,
- standard:no-line-break-before-assignment,
- standard:no-multi-spaces,
- standard:no-semi,
- standard:no-trailing-spaces,
- standard:no-unit-return,
- standard:no-unused-imports,
- standard:no-wildcard-imports,
- standard:op-spacing,
- standard:parameter-list-wrapping,
- standard:paren-spacing,
- standard:range-spacing,
- standard:string-template,
- standard:indent,
- standard:max-line-length
[DEBUG] Checking /Users/tom/temp/a.kt
Resolving .editorconfig files for /Users/tom/temp/a.kt file path
Loaded .editorconfig: []
/Users/tom/temp/a.kt:1:1: class MyException should be declared in a file named MyException.kt (cannot be auto-corrected)
/Users/tom/temp/a.kt:4:1: Unexpected indentation (4) (should be 0)
[DEBUG] 784ms / 1 file(s) / 2 error(s)
``` | non_defect | add new rule to rewrite the class signature edit i can workaround by avoiding writing code like this instead let the constructor be at the same line with class name i just want to report it so you can know that it happens but please make this a low priority hi thanks for the lib for the following code intellij idea thinks there should be spaces at message string while ktlint thinks cat temp a kt java jar users tom opt ktlint all jar temp a kt debug package hello class myexception message string runtimeexception message discovered reporter with baseline id discovered reporter with checkstyle id discovered reporter with json id discovered reporter with html id discovered reporter with plain id discovered reporter with sarif id initializing plain reporter with verbose false color false color name dark gray rule with id standard max line length should run after the rule with id experimental trailing comma however the latter rule is not loaded and is allowed to be ignored for best results it is advised load the rule rules will be executed in order below unless disabled standard filename standard final newline standard chain wrapping standard colon spacing standard comma spacing standard comment spacing standard curly spacing standard dot spacing standard import ordering standard keyword spacing standard modifier order standard no blank line before rbrace standard no consecutive blank lines standard no empty class body standard no line break after else standard no line break before assignment standard no multi spaces standard no semi standard no trailing spaces standard no unit return standard no unused imports standard no wildcard imports standard op spacing standard parameter list wrapping standard paren spacing standard range spacing standard string template standard indent standard max line length checking users tom temp a kt resolving editorconfig files for users tom temp a kt file path loaded editorconfig users tom temp a kt class myexception should be declared in a file named myexception kt cannot be auto corrected users tom temp a kt unexpected indentation should be file s error s | 0 |
303,126 | 22,954,976,367 | IssuesEvent | 2022-07-19 10:42:47 | daybrush/moveable | https://api.github.com/repos/daybrush/moveable | closed | [docs] it shoud be useResizeObserver not Zoom | documentation complete | ## Environments
------------------------------
- Operating System: `Darwin`
- Node Version: `v16.15.1`
- Package Manager: `yarn@1.22.19`
- movable version: `"vue-moveable": "^2.0.0-beta.5",`
------------------------------
## Description
just a small typo in there, where it shoud be `useResizeObserver` not `Zoom`

| 1.0 | [docs] it shoud be useResizeObserver not Zoom - ## Environments
------------------------------
- Operating System: `Darwin`
- Node Version: `v16.15.1`
- Package Manager: `yarn@1.22.19`
- movable version: `"vue-moveable": "^2.0.0-beta.5",`
------------------------------
## Description
just a small typo in there, where it shoud be `useResizeObserver` not `Zoom`

| non_defect | it shoud be useresizeobserver not zoom environments operating system darwin node version package manager yarn movable version vue moveable beta description just a small typo in there where it shoud be useresizeobserver not zoom | 0 |
16,846 | 2,948,327,330 | IssuesEvent | 2015-07-06 01:35:43 | Winetricks/winetricks | https://api.github.com/repos/Winetricks/winetricks | closed | configuration file | auto-migrated Priority-Medium Type-Defect | ```
maybe a .winetricksrc ?
where we can set default options, like prefix root, use --isolate as default,
etc.
tnx.
```
Original issue reported on code.google.com by `mail2dny@gmail.com` on 9 Apr 2011 at 10:07 | 1.0 | configuration file - ```
maybe a .winetricksrc ?
where we can set default options, like prefix root, use --isolate as default,
etc.
tnx.
```
Original issue reported on code.google.com by `mail2dny@gmail.com` on 9 Apr 2011 at 10:07 | defect | configuration file maybe a winetricksrc where we can set default options like prefix root use isolate as default etc tnx original issue reported on code google com by gmail com on apr at | 1 |
636,391 | 20,599,159,029 | IssuesEvent | 2022-03-06 01:06:58 | ut-code/utmap-times | https://api.github.com/repos/ut-code/utmap-times | closed | graduates詳細の写真挿入を中央寄せにする | bug Priority: High | graduates詳細で写真を挿入した際に、左寄せになってしまうので、中央寄せにしたいです。
<img width="930" alt="スクリーンショット 2022-03-01 18 24 57" src="https://user-images.githubusercontent.com/80612908/156141806-111a5812-2b0b-429c-86d1-d12c942e58db.png">
| 1.0 | graduates詳細の写真挿入を中央寄せにする - graduates詳細で写真を挿入した際に、左寄せになってしまうので、中央寄せにしたいです。
<img width="930" alt="スクリーンショット 2022-03-01 18 24 57" src="https://user-images.githubusercontent.com/80612908/156141806-111a5812-2b0b-429c-86d1-d12c942e58db.png">
| non_defect | graduates詳細の写真挿入を中央寄せにする graduates詳細で写真を挿入した際に、左寄せになってしまうので、中央寄せにしたいです。 img width alt スクリーンショット src | 0 |
120,591 | 25,827,480,150 | IssuesEvent | 2022-12-12 13:58:12 | apache/incubator-baremaps | https://api.github.com/repos/apache/incubator-baremaps | closed | Including the Geocoder in an example web application | enhancement geocoder | For now we can only use the Geocoder as a library or query it through the CLI. It would be nice for an example to have a simple web application to demo it and maybe to include it with a map.
It should consist of two parts:
- A REST endpoint that can query an address and return a location.
- A HTML web page that can query the endpoint to demo the service. | 1.0 | Including the Geocoder in an example web application - For now we can only use the Geocoder as a library or query it through the CLI. It would be nice for an example to have a simple web application to demo it and maybe to include it with a map.
It should consist of two parts:
- A REST endpoint that can query an address and return a location.
- A HTML web page that can query the endpoint to demo the service. | non_defect | including the geocoder in an example web application for now we can only use the geocoder as a library or query it through the cli it would be nice for an example to have a simple web application to demo it and maybe to include it with a map it should consist of two parts a rest endpoint that can query an address and return a location a html web page that can query the endpoint to demo the service | 0 |
9,436 | 2,615,150,058 | IssuesEvent | 2015-03-01 06:27:14 | chrsmith/reaver-wps | https://api.github.com/repos/chrsmith/reaver-wps | closed | Failed to associate | auto-migrated Priority-Triage Type-Defect | ```
0. What version of Reaver are you using? (Only defects against the latest
version will be considered.)
reaver 1.3
1. What operating system are you using (Linux is the only supported OS)?
backtrack 5R1 runing on vmplayer(by using a boot CD I have the same issue)
uname -a
linux bt 2.6.39.4
2. Is your wireless card in monitor mode (yes/no)?
yes
3. What is the signal strength of the Access Point you are trying to crack?
very strong the AP is next to the wireless card..it is my router
PWR is -26 in airodump output
4. What is the manufacturer and model # of the device you are trying to
crack?
a 2wire 2701HG-G router
5. What is the entire command line string you are supplying to reaver?
reaver -i mon 0 -b 00:26:50:47:4A:19
6. Please describe what you think the issue is.
Failed to associate error
7. Paste the output from Reaver below.
View image : http://www.picpaste.com/BT5R1-JAeJJKPx.jpg
```
Original issue reported on code.google.com by `voleuse....@gmail.com` on 16 Jan 2012 at 5:10 | 1.0 | Failed to associate - ```
0. What version of Reaver are you using? (Only defects against the latest
version will be considered.)
reaver 1.3
1. What operating system are you using (Linux is the only supported OS)?
backtrack 5R1 runing on vmplayer(by using a boot CD I have the same issue)
uname -a
linux bt 2.6.39.4
2. Is your wireless card in monitor mode (yes/no)?
yes
3. What is the signal strength of the Access Point you are trying to crack?
very strong the AP is next to the wireless card..it is my router
PWR is -26 in airodump output
4. What is the manufacturer and model # of the device you are trying to
crack?
a 2wire 2701HG-G router
5. What is the entire command line string you are supplying to reaver?
reaver -i mon 0 -b 00:26:50:47:4A:19
6. Please describe what you think the issue is.
Failed to associate error
7. Paste the output from Reaver below.
View image : http://www.picpaste.com/BT5R1-JAeJJKPx.jpg
```
Original issue reported on code.google.com by `voleuse....@gmail.com` on 16 Jan 2012 at 5:10 | defect | failed to associate what version of reaver are you using only defects against the latest version will be considered reaver what operating system are you using linux is the only supported os backtrack runing on vmplayer by using a boot cd i have the same issue uname a linux bt is your wireless card in monitor mode yes no yes what is the signal strength of the access point you are trying to crack very strong the ap is next to the wireless card it is my router pwr is in airodump output what is the manufacturer and model of the device you are trying to crack a g router what is the entire command line string you are supplying to reaver reaver i mon b please describe what you think the issue is failed to associate error paste the output from reaver below view image original issue reported on code google com by voleuse gmail com on jan at | 1 |
287,969 | 24,878,810,843 | IssuesEvent | 2022-10-27 21:53:37 | ImagingDataCommons/IDC-WebApp | https://api.github.com/repos/ImagingDataCommons/IDC-WebApp | closed | Test and Prod tiers show search scope temp instead of search scope | bug testing needed testing passed priority In Progress | Identified by Bill L while discussing UX designs
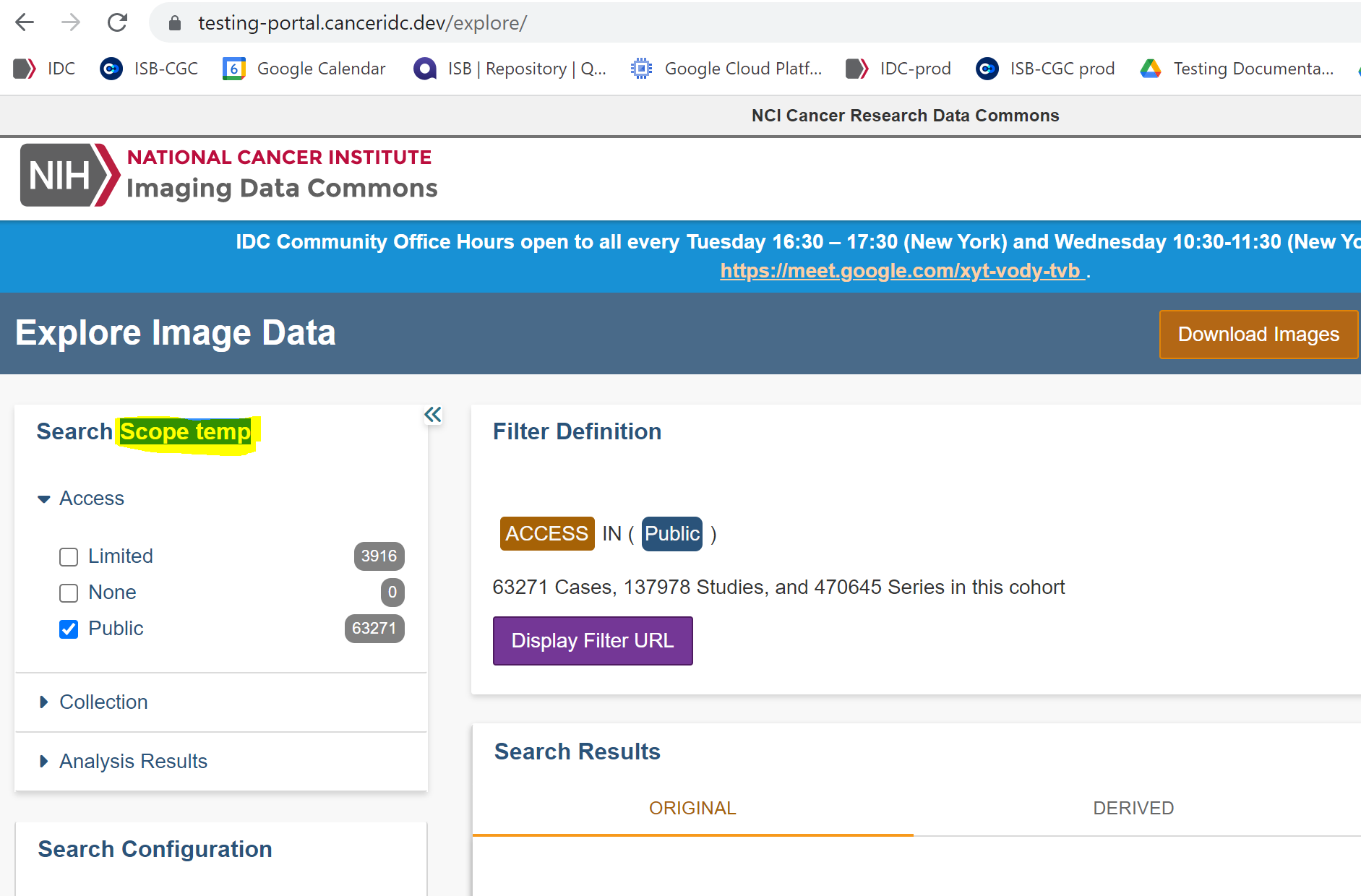
| 2.0 | Test and Prod tiers show search scope temp instead of search scope - Identified by Bill L while discussing UX designs
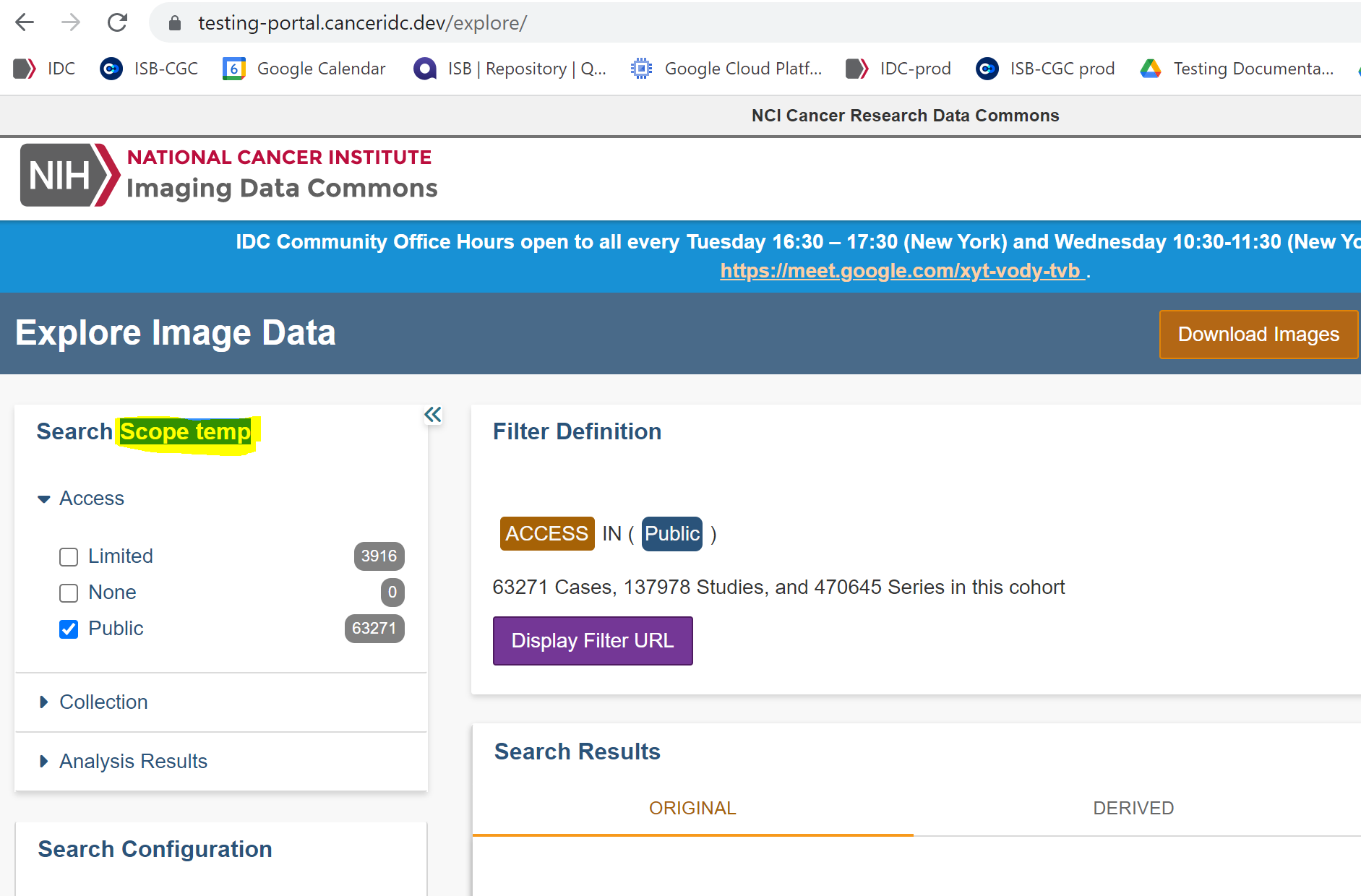
| non_defect | test and prod tiers show search scope temp instead of search scope identified by bill l while discussing ux designs | 0 |
67,675 | 21,048,061,108 | IssuesEvent | 2022-03-31 17:58:40 | jlaffaye/ftp | https://api.github.com/repos/jlaffaye/ftp | opened | Timeout when using ftps to invoke .List and .NameList (TLS) | defect | **Describe the bug**
Timeout when using `ftps` to invoke `.List` and `.NameList`. Error is "context deadline exceeded".
Maybe (??) related to an underlying TLS issue - possibly #249 and #252
**To Reproduce**
```
c, err = ftp.Dial(
ftpsString,
ftp.DialWithTimeout(time.Duration(20)*time.Second), // 20 seconds is default for Filezilla.
ftp.DialWithExplicitTLS(&tls.Config{InsecureSkipVerify: true}),
ftp.DialWithDisabledEPSV(true), // both true and false have same error 'context deadline exceeded'
)
// c.Login, as applicable
entries, err := c.List("/dir-to-access") // or use "/" ... same error
if err != nil {
return err // context deadline exceeded
}
```
**Expected behavior**
The list of file names should be retrieved.
**FTP server**
- [Globalscape]([https://www.globalscape.com/) v3.63 - uncertain which product
- Public URL: n/a
**Debug output**
```
220 Welcome to XXXX.XXXXX.XXX
USER user@example.com
331 Password required for user@example.com.
PASS XXXXXXXXXXXX
230 Login OK. Proceed.
FEAT
211-Features supported:
COMB target;source_list
REST STREAM
SIZE
MDTM
MFMT
XCRC filename;start;end
SSCN
MLST Size*;Modify*;Create;Type*;Unique;Perm*;Lang;Media-Type;CharSet;
MODE Z
XNOP
UTF8
UTF-8
LANG EN*
CLNT
211 END
TYPE I
200 Type set to I.
OPTS UTF8 ON
200 Entering UTF-8 mode.
PBSZ 0
200 PBSZ Command OK. Protection buffer size set to 0.
PROT P
200 PROT Command OK. Using Private data connection.
PWD
257 "/" is current folder.
PASV
227 Entering Passive Mode (74,51,209,105,82,8).
failed to list entries of ftp server path '/LCRECData (IT.BIData)'; context deadline exceeded
```
Below is output from within Filezilla from the same development workstation.
Filezilla successfully connects and lists the directory.
The command that fails is MLST beginning at [ftp.line-619](https://github.com/jlaffaye/ftp/blob/d2c44e311e789ae81d35465a42498bc08f521108/ftp.go#L619) but error occurs lower when issued to the server.
**Additional context**
```
Command: PWD
Trace: tls_layer_impl::on_read()
Trace: CFtpControlSocket::OnReceive()
Response: 257 "/" is current folder.
Trace: CFtpChangeDirOpData::ParseResponse() in state 1
Trace: CFtpControlSocket::ResetOperation(0)
Trace: CControlSocket::ResetOperation(0)
Trace: CFtpChangeDirOpData::Reset(0) in state 1
Trace: CFtpListOpData::SubcommandResult(0) in state 1
Trace: CControlSocket::SendNextCommand()
Trace: CFtpListOpData::Send() in state 2
Trace: CFtpRawTransferOpData::Send() in state 0
Trace: CFtpRawTransferOpData::Send() in state 1
Command: TYPE I
Trace: tls_layer_impl::on_read()
Trace: CFtpControlSocket::OnReceive()
Response: 200 Type set to I.
Trace: CFtpRawTransferOpData::ParseResponse() in state 1
Trace: CControlSocket::SendNextCommand()
Trace: CFtpRawTransferOpData::Send() in state 2
Command: PASV
Trace: tls_layer_impl::on_read()
Trace: CFtpControlSocket::OnReceive()
Response: 227 Entering Passive Mode (74,51,209,105,82,8).
Trace: CFtpRawTransferOpData::ParseResponse() in state 2
Trace: CControlSocket::SendNextCommand()
Trace: CFtpRawTransferOpData::Send() in state 4
Trace: Binding data connection source IP to control connection source IP XXX.XXX.XXX.XXX
Trace: tls_layer_impl::client_handshake()
Trace: Trying to resume existing TLS session.
THIS COMMAND "MLSD" IS WHERE THE TIMEOUT ERROR IS HAPPENING.
IT IS ASSIGNED IN THE CLIENT in ftp.go, line 619, AND ERROS WHEN ISSUED TO THE SERVER,
BUT IN FILEZILLA IT WORKS FINE.
Command: MLSD
Trace: tls_layer_impl::on_read()
Trace: CFtpControlSocket::OnReceive()
Response: 150 Opening BINARY mode data connection for MLSD /.
Trace: CFtpRawTransferOpData::ParseResponse() in state 4
Trace: CControlSocket::SendNextCommand()
Trace: CFtpRawTransferOpData::Send() in state 5
Trace: tls_layer_impl::on_send()
Trace: tls_layer_impl::continue_handshake()
Trace: TLS handshake: About to send CLIENT HELLO
Trace: TLS handshake: Sent CLIENT HELLO
Trace: tls_layer_impl::on_read()
Trace: tls_layer_impl::continue_handshake()
Trace: TLS handshake: Received SERVER HELLO
Trace: TLS handshake: Processed SERVER HELLO
Trace: TLS handshake: Received FINISHED
Trace: TLS handshake: Processed FINISHED
Trace: TLS handshake: About to send FINISHED
Trace: TLS handshake: Sent FINISHED
Trace: TLS Handshake successful
Trace: TLS Session resumed
Trace: Protocol: TLS1.2, Key exchange: ECDHE-SECP256R1, Cipher: AES-256-GCM, MAC: AEAD
Trace: tls_layer_impl::verify_certificate()
Trace: CTransferSocket::OnConnect
Trace: CTransferSocket::OnReceive(), m_transferMode=0
Trace: tls_layer_impl::on_read()
Trace: CTransferSocket::OnReceive(), m_transferMode=0
Trace: tls_layer_impl::on_read()
Trace: CFtpControlSocket::OnReceive()
Response: 226 Transfer complete. 136 bytes transferred. 136 bps.
Trace: CFtpRawTransferOpData::ParseResponse() in state 5
Trace: CControlSocket::SendNextCommand()
Trace: CFtpRawTransferOpData::Send() in state 8
Trace: tls_layer_impl::on_read()
Trace: CTransferSocket::OnReceive(), m_transferMode=0
Trace: CTransferSocket::TransferEnd(1)
Trace: tls_layer_impl::shutdown()
Trace: tls_layer_impl::continue_shutdown()
Trace: CFtpControlSocket::TransferEnd()
Trace: CFtpControlSocket::ResetOperation(0)
Trace: CControlSocket::ResetOperation(0)
Trace: CFtpRawTransferOpData::Reset(0) in state 8
Trace: CFtpListOpData::SubcommandResult(0) in state 3
Trace: CFtpControlSocket::ResetOperation(0)
Trace: CControlSocket::ResetOperation(0)
Trace: CFtpListOpData::Reset(0) in state 3
Status: Directory listing of "/" successful
Trace: CFileZillaEnginePrivate::ResetOperation(0)
Trace: CControlSocket::SendNextCommand()
Trace: CFtpListOpData::Send() in state 0
Status: Retrieving directory listing of "/MY DIRECTORY"...
Trace: CFtpChangeDirOpData::Send() in state 0
Trace: CFtpChangeDirOpData::Send() in state 2
Command: CWD /MY DIRECTORY
Trace: tls_layer_impl::on_read()
Trace: CFtpControlSocket::OnReceive()
Response: 250 Folder changed to "/MY DIRECTORY".
Trace: CFtpChangeDirOpData::ParseResponse() in state 2
Trace: CFtpControlSocket::ResetOperation(0)
Trace: CControlSocket::ResetOperation(0)
Trace: CFtpChangeDirOpData::Reset(0) in state 2
Trace: CFtpListOpData::SubcommandResult(0) in state 1
Trace: CControlSocket::SendNextCommand()
Trace: CFtpListOpData::Send() in state 2
Trace: CFtpRawTransferOpData::Send() in state 0
Trace: CFtpRawTransferOpData::Send() in state 2
Command: PASV
Trace: tls_layer_impl::on_read()
Trace: CFtpControlSocket::OnReceive()
Response: 227 Entering Passive Mode (74,51,209,105,82,18).
Trace: CFtpRawTransferOpData::ParseResponse() in state 2
Trace: CControlSocket::SendNextCommand()
Trace: CFtpRawTransferOpData::Send() in state 4
Trace: Binding data connection source IP to control connection source IP 10.183.44.57
Trace: tls_layer_impl::client_handshake()
Trace: Trying to resume existing TLS session.
Command: MLSD
Trace: tls_layer_impl::on_send()
Trace: tls_layer_impl::continue_handshake()
Trace: TLS handshake: About to send CLIENT HELLO
Trace: TLS handshake: Sent CLIENT HELLO
Trace: tls_layer_impl::on_read()
Trace: CFtpControlSocket::OnReceive()
Response: 150 Opening BINARY mode data connection for MLSD /MY DIRECTORY.
Trace: CFtpRawTransferOpData::ParseResponse() in state 4
Trace: CControlSocket::SendNextCommand()
Trace: CFtpRawTransferOpData::Send() in state 5
Trace: tls_layer_impl::on_read()
Trace: tls_layer_impl::continue_handshake()
Trace: TLS handshake: Received SERVER HELLO
Trace: TLS handshake: Processed SERVER HELLO
Trace: TLS handshake: Received FINISHED
Trace: TLS handshake: Processed FINISHED
Trace: TLS handshake: About to send FINISHED
Trace: TLS handshake: Sent FINISHED
Trace: TLS Handshake successful
Trace: TLS Session resumed
Trace: Protocol: TLS1.2, Key exchange: ECDHE-SECP256R1, Cipher: AES-256-GCM, MAC: AEAD
Trace: tls_layer_impl::verify_certificate()
Trace: CTransferSocket::OnConnect
Trace: CTransferSocket::OnReceive(), m_transferMode=0
Trace: tls_layer_impl::on_read()
Trace: CTransferSocket::OnReceive(), m_transferMode=0
Trace: tls_layer_impl::on_read()
Trace: CTransferSocket::OnReceive(), m_transferMode=0
Trace: CTransferSocket::TransferEnd(1)
Trace: tls_layer_impl::shutdown()
Trace: tls_layer_impl::continue_shutdown()
Trace: CFtpControlSocket::TransferEnd()
Trace: tls_layer_impl::on_read()
Trace: CFtpControlSocket::OnReceive()
Response: 226 Transfer complete. 2889 bytes transferred. 2889 bps.
Trace: CFtpRawTransferOpData::ParseResponse() in state 7
Trace: CFtpControlSocket::ResetOperation(0)
Trace: CControlSocket::ResetOperation(0)
Trace: CFtpRawTransferOpData::Reset(0) in state 7
Trace: CFtpListOpData::SubcommandResult(0) in state 3
Trace: CFtpControlSocket::ResetOperation(0)
Trace: CControlSocket::ResetOperation(0)
Trace: CFtpListOpData::Reset(0) in state 3
Status: Directory listing of "/MY DIRECTORY" successful
``` | 1.0 | Timeout when using ftps to invoke .List and .NameList (TLS) - **Describe the bug**
Timeout when using `ftps` to invoke `.List` and `.NameList`. Error is "context deadline exceeded".
Maybe (??) related to an underlying TLS issue - possibly #249 and #252
**To Reproduce**
```
c, err = ftp.Dial(
ftpsString,
ftp.DialWithTimeout(time.Duration(20)*time.Second), // 20 seconds is default for Filezilla.
ftp.DialWithExplicitTLS(&tls.Config{InsecureSkipVerify: true}),
ftp.DialWithDisabledEPSV(true), // both true and false have same error 'context deadline exceeded'
)
// c.Login, as applicable
entries, err := c.List("/dir-to-access") // or use "/" ... same error
if err != nil {
return err // context deadline exceeded
}
```
**Expected behavior**
The list of file names should be retrieved.
**FTP server**
- [Globalscape]([https://www.globalscape.com/) v3.63 - uncertain which product
- Public URL: n/a
**Debug output**
```
220 Welcome to XXXX.XXXXX.XXX
USER user@example.com
331 Password required for user@example.com.
PASS XXXXXXXXXXXX
230 Login OK. Proceed.
FEAT
211-Features supported:
COMB target;source_list
REST STREAM
SIZE
MDTM
MFMT
XCRC filename;start;end
SSCN
MLST Size*;Modify*;Create;Type*;Unique;Perm*;Lang;Media-Type;CharSet;
MODE Z
XNOP
UTF8
UTF-8
LANG EN*
CLNT
211 END
TYPE I
200 Type set to I.
OPTS UTF8 ON
200 Entering UTF-8 mode.
PBSZ 0
200 PBSZ Command OK. Protection buffer size set to 0.
PROT P
200 PROT Command OK. Using Private data connection.
PWD
257 "/" is current folder.
PASV
227 Entering Passive Mode (74,51,209,105,82,8).
failed to list entries of ftp server path '/LCRECData (IT.BIData)'; context deadline exceeded
```
Below is output from within Filezilla from the same development workstation.
Filezilla successfully connects and lists the directory.
The command that fails is MLST beginning at [ftp.line-619](https://github.com/jlaffaye/ftp/blob/d2c44e311e789ae81d35465a42498bc08f521108/ftp.go#L619) but error occurs lower when issued to the server.
**Additional context**
```
Command: PWD
Trace: tls_layer_impl::on_read()
Trace: CFtpControlSocket::OnReceive()
Response: 257 "/" is current folder.
Trace: CFtpChangeDirOpData::ParseResponse() in state 1
Trace: CFtpControlSocket::ResetOperation(0)
Trace: CControlSocket::ResetOperation(0)
Trace: CFtpChangeDirOpData::Reset(0) in state 1
Trace: CFtpListOpData::SubcommandResult(0) in state 1
Trace: CControlSocket::SendNextCommand()
Trace: CFtpListOpData::Send() in state 2
Trace: CFtpRawTransferOpData::Send() in state 0
Trace: CFtpRawTransferOpData::Send() in state 1
Command: TYPE I
Trace: tls_layer_impl::on_read()
Trace: CFtpControlSocket::OnReceive()
Response: 200 Type set to I.
Trace: CFtpRawTransferOpData::ParseResponse() in state 1
Trace: CControlSocket::SendNextCommand()
Trace: CFtpRawTransferOpData::Send() in state 2
Command: PASV
Trace: tls_layer_impl::on_read()
Trace: CFtpControlSocket::OnReceive()
Response: 227 Entering Passive Mode (74,51,209,105,82,8).
Trace: CFtpRawTransferOpData::ParseResponse() in state 2
Trace: CControlSocket::SendNextCommand()
Trace: CFtpRawTransferOpData::Send() in state 4
Trace: Binding data connection source IP to control connection source IP XXX.XXX.XXX.XXX
Trace: tls_layer_impl::client_handshake()
Trace: Trying to resume existing TLS session.
THIS COMMAND "MLSD" IS WHERE THE TIMEOUT ERROR IS HAPPENING.
IT IS ASSIGNED IN THE CLIENT in ftp.go, line 619, AND ERROS WHEN ISSUED TO THE SERVER,
BUT IN FILEZILLA IT WORKS FINE.
Command: MLSD
Trace: tls_layer_impl::on_read()
Trace: CFtpControlSocket::OnReceive()
Response: 150 Opening BINARY mode data connection for MLSD /.
Trace: CFtpRawTransferOpData::ParseResponse() in state 4
Trace: CControlSocket::SendNextCommand()
Trace: CFtpRawTransferOpData::Send() in state 5
Trace: tls_layer_impl::on_send()
Trace: tls_layer_impl::continue_handshake()
Trace: TLS handshake: About to send CLIENT HELLO
Trace: TLS handshake: Sent CLIENT HELLO
Trace: tls_layer_impl::on_read()
Trace: tls_layer_impl::continue_handshake()
Trace: TLS handshake: Received SERVER HELLO
Trace: TLS handshake: Processed SERVER HELLO
Trace: TLS handshake: Received FINISHED
Trace: TLS handshake: Processed FINISHED
Trace: TLS handshake: About to send FINISHED
Trace: TLS handshake: Sent FINISHED
Trace: TLS Handshake successful
Trace: TLS Session resumed
Trace: Protocol: TLS1.2, Key exchange: ECDHE-SECP256R1, Cipher: AES-256-GCM, MAC: AEAD
Trace: tls_layer_impl::verify_certificate()
Trace: CTransferSocket::OnConnect
Trace: CTransferSocket::OnReceive(), m_transferMode=0
Trace: tls_layer_impl::on_read()
Trace: CTransferSocket::OnReceive(), m_transferMode=0
Trace: tls_layer_impl::on_read()
Trace: CFtpControlSocket::OnReceive()
Response: 226 Transfer complete. 136 bytes transferred. 136 bps.
Trace: CFtpRawTransferOpData::ParseResponse() in state 5
Trace: CControlSocket::SendNextCommand()
Trace: CFtpRawTransferOpData::Send() in state 8
Trace: tls_layer_impl::on_read()
Trace: CTransferSocket::OnReceive(), m_transferMode=0
Trace: CTransferSocket::TransferEnd(1)
Trace: tls_layer_impl::shutdown()
Trace: tls_layer_impl::continue_shutdown()
Trace: CFtpControlSocket::TransferEnd()
Trace: CFtpControlSocket::ResetOperation(0)
Trace: CControlSocket::ResetOperation(0)
Trace: CFtpRawTransferOpData::Reset(0) in state 8
Trace: CFtpListOpData::SubcommandResult(0) in state 3
Trace: CFtpControlSocket::ResetOperation(0)
Trace: CControlSocket::ResetOperation(0)
Trace: CFtpListOpData::Reset(0) in state 3
Status: Directory listing of "/" successful
Trace: CFileZillaEnginePrivate::ResetOperation(0)
Trace: CControlSocket::SendNextCommand()
Trace: CFtpListOpData::Send() in state 0
Status: Retrieving directory listing of "/MY DIRECTORY"...
Trace: CFtpChangeDirOpData::Send() in state 0
Trace: CFtpChangeDirOpData::Send() in state 2
Command: CWD /MY DIRECTORY
Trace: tls_layer_impl::on_read()
Trace: CFtpControlSocket::OnReceive()
Response: 250 Folder changed to "/MY DIRECTORY".
Trace: CFtpChangeDirOpData::ParseResponse() in state 2
Trace: CFtpControlSocket::ResetOperation(0)
Trace: CControlSocket::ResetOperation(0)
Trace: CFtpChangeDirOpData::Reset(0) in state 2
Trace: CFtpListOpData::SubcommandResult(0) in state 1
Trace: CControlSocket::SendNextCommand()
Trace: CFtpListOpData::Send() in state 2
Trace: CFtpRawTransferOpData::Send() in state 0
Trace: CFtpRawTransferOpData::Send() in state 2
Command: PASV
Trace: tls_layer_impl::on_read()
Trace: CFtpControlSocket::OnReceive()
Response: 227 Entering Passive Mode (74,51,209,105,82,18).
Trace: CFtpRawTransferOpData::ParseResponse() in state 2
Trace: CControlSocket::SendNextCommand()
Trace: CFtpRawTransferOpData::Send() in state 4
Trace: Binding data connection source IP to control connection source IP 10.183.44.57
Trace: tls_layer_impl::client_handshake()
Trace: Trying to resume existing TLS session.
Command: MLSD
Trace: tls_layer_impl::on_send()
Trace: tls_layer_impl::continue_handshake()
Trace: TLS handshake: About to send CLIENT HELLO
Trace: TLS handshake: Sent CLIENT HELLO
Trace: tls_layer_impl::on_read()
Trace: CFtpControlSocket::OnReceive()
Response: 150 Opening BINARY mode data connection for MLSD /MY DIRECTORY.
Trace: CFtpRawTransferOpData::ParseResponse() in state 4
Trace: CControlSocket::SendNextCommand()
Trace: CFtpRawTransferOpData::Send() in state 5
Trace: tls_layer_impl::on_read()
Trace: tls_layer_impl::continue_handshake()
Trace: TLS handshake: Received SERVER HELLO
Trace: TLS handshake: Processed SERVER HELLO
Trace: TLS handshake: Received FINISHED
Trace: TLS handshake: Processed FINISHED
Trace: TLS handshake: About to send FINISHED
Trace: TLS handshake: Sent FINISHED
Trace: TLS Handshake successful
Trace: TLS Session resumed
Trace: Protocol: TLS1.2, Key exchange: ECDHE-SECP256R1, Cipher: AES-256-GCM, MAC: AEAD
Trace: tls_layer_impl::verify_certificate()
Trace: CTransferSocket::OnConnect
Trace: CTransferSocket::OnReceive(), m_transferMode=0
Trace: tls_layer_impl::on_read()
Trace: CTransferSocket::OnReceive(), m_transferMode=0
Trace: tls_layer_impl::on_read()
Trace: CTransferSocket::OnReceive(), m_transferMode=0
Trace: CTransferSocket::TransferEnd(1)
Trace: tls_layer_impl::shutdown()
Trace: tls_layer_impl::continue_shutdown()
Trace: CFtpControlSocket::TransferEnd()
Trace: tls_layer_impl::on_read()
Trace: CFtpControlSocket::OnReceive()
Response: 226 Transfer complete. 2889 bytes transferred. 2889 bps.
Trace: CFtpRawTransferOpData::ParseResponse() in state 7
Trace: CFtpControlSocket::ResetOperation(0)
Trace: CControlSocket::ResetOperation(0)
Trace: CFtpRawTransferOpData::Reset(0) in state 7
Trace: CFtpListOpData::SubcommandResult(0) in state 3
Trace: CFtpControlSocket::ResetOperation(0)
Trace: CControlSocket::ResetOperation(0)
Trace: CFtpListOpData::Reset(0) in state 3
Status: Directory listing of "/MY DIRECTORY" successful
``` | defect | timeout when using ftps to invoke list and namelist tls describe the bug timeout when using ftps to invoke list and namelist error is context deadline exceeded maybe related to an underlying tls issue possibly and to reproduce c err ftp dial ftpsstring ftp dialwithtimeout time duration time second seconds is default for filezilla ftp dialwithexplicittls tls config insecureskipverify true ftp dialwithdisabledepsv true both true and false have same error context deadline exceeded c login as applicable entries err c list dir to access or use same error if err nil return err context deadline exceeded expected behavior the list of file names should be retrieved ftp server uncertain which product public url n a debug output welcome to xxxx xxxxx xxx user user example com password required for user example com pass xxxxxxxxxxxx login ok proceed feat features supported comb target source list rest stream size mdtm mfmt xcrc filename start end sscn mlst size modify create type unique perm lang media type charset mode z xnop utf lang en clnt end type i type set to i opts on entering utf mode pbsz pbsz command ok protection buffer size set to prot p prot command ok using private data connection pwd is current folder pasv entering passive mode failed to list entries of ftp server path lcrecdata it bidata context deadline exceeded below is output from within filezilla from the same development workstation filezilla successfully connects and lists the directory the command that fails is mlst beginning at but error occurs lower when issued to the server additional context command pwd trace tls layer impl on read trace cftpcontrolsocket onreceive response is current folder trace cftpchangediropdata parseresponse in state trace cftpcontrolsocket resetoperation trace ccontrolsocket resetoperation trace cftpchangediropdata reset in state trace cftplistopdata subcommandresult in state trace ccontrolsocket sendnextcommand trace cftplistopdata send in state trace cftprawtransferopdata send in state trace cftprawtransferopdata send in state command type i trace tls layer impl on read trace cftpcontrolsocket onreceive response type set to i trace cftprawtransferopdata parseresponse in state trace ccontrolsocket sendnextcommand trace cftprawtransferopdata send in state command pasv trace tls layer impl on read trace cftpcontrolsocket onreceive response entering passive mode trace cftprawtransferopdata parseresponse in state trace ccontrolsocket sendnextcommand trace cftprawtransferopdata send in state trace binding data connection source ip to control connection source ip xxx xxx xxx xxx trace tls layer impl client handshake trace trying to resume existing tls session this command mlsd is where the timeout error is happening it is assigned in the client in ftp go line and erros when issued to the server but in filezilla it works fine command mlsd trace tls layer impl on read trace cftpcontrolsocket onreceive response opening binary mode data connection for mlsd trace cftprawtransferopdata parseresponse in state trace ccontrolsocket sendnextcommand trace cftprawtransferopdata send in state trace tls layer impl on send trace tls layer impl continue handshake trace tls handshake about to send client hello trace tls handshake sent client hello trace tls layer impl on read trace tls layer impl continue handshake trace tls handshake received server hello trace tls handshake processed server hello trace tls handshake received finished trace tls handshake processed finished trace tls handshake about to send finished trace tls handshake sent finished trace tls handshake successful trace tls session resumed trace protocol key exchange ecdhe cipher aes gcm mac aead trace tls layer impl verify certificate trace ctransfersocket onconnect trace ctransfersocket onreceive m transfermode trace tls layer impl on read trace ctransfersocket onreceive m transfermode trace tls layer impl on read trace cftpcontrolsocket onreceive response transfer complete bytes transferred bps trace cftprawtransferopdata parseresponse in state trace ccontrolsocket sendnextcommand trace cftprawtransferopdata send in state trace tls layer impl on read trace ctransfersocket onreceive m transfermode trace ctransfersocket transferend trace tls layer impl shutdown trace tls layer impl continue shutdown trace cftpcontrolsocket transferend trace cftpcontrolsocket resetoperation trace ccontrolsocket resetoperation trace cftprawtransferopdata reset in state trace cftplistopdata subcommandresult in state trace cftpcontrolsocket resetoperation trace ccontrolsocket resetoperation trace cftplistopdata reset in state status directory listing of successful trace cfilezillaengineprivate resetoperation trace ccontrolsocket sendnextcommand trace cftplistopdata send in state status retrieving directory listing of my directory trace cftpchangediropdata send in state trace cftpchangediropdata send in state command cwd my directory trace tls layer impl on read trace cftpcontrolsocket onreceive response folder changed to my directory trace cftpchangediropdata parseresponse in state trace cftpcontrolsocket resetoperation trace ccontrolsocket resetoperation trace cftpchangediropdata reset in state trace cftplistopdata subcommandresult in state trace ccontrolsocket sendnextcommand trace cftplistopdata send in state trace cftprawtransferopdata send in state trace cftprawtransferopdata send in state command pasv trace tls layer impl on read trace cftpcontrolsocket onreceive response entering passive mode trace cftprawtransferopdata parseresponse in state trace ccontrolsocket sendnextcommand trace cftprawtransferopdata send in state trace binding data connection source ip to control connection source ip trace tls layer impl client handshake trace trying to resume existing tls session command mlsd trace tls layer impl on send trace tls layer impl continue handshake trace tls handshake about to send client hello trace tls handshake sent client hello trace tls layer impl on read trace cftpcontrolsocket onreceive response opening binary mode data connection for mlsd my directory trace cftprawtransferopdata parseresponse in state trace ccontrolsocket sendnextcommand trace cftprawtransferopdata send in state trace tls layer impl on read trace tls layer impl continue handshake trace tls handshake received server hello trace tls handshake processed server hello trace tls handshake received finished trace tls handshake processed finished trace tls handshake about to send finished trace tls handshake sent finished trace tls handshake successful trace tls session resumed trace protocol key exchange ecdhe cipher aes gcm mac aead trace tls layer impl verify certificate trace ctransfersocket onconnect trace ctransfersocket onreceive m transfermode trace tls layer impl on read trace ctransfersocket onreceive m transfermode trace tls layer impl on read trace ctransfersocket onreceive m transfermode trace ctransfersocket transferend trace tls layer impl shutdown trace tls layer impl continue shutdown trace cftpcontrolsocket transferend trace tls layer impl on read trace cftpcontrolsocket onreceive response transfer complete bytes transferred bps trace cftprawtransferopdata parseresponse in state trace cftpcontrolsocket resetoperation trace ccontrolsocket resetoperation trace cftprawtransferopdata reset in state trace cftplistopdata subcommandresult in state trace cftpcontrolsocket resetoperation trace ccontrolsocket resetoperation trace cftplistopdata reset in state status directory listing of my directory successful | 1 |
38,465 | 8,825,116,169 | IssuesEvent | 2019-01-02 19:36:41 | scipy/scipy | https://api.github.com/repos/scipy/scipy | closed | rv_sample accepts invalid input in scipy.stats | defect good first issue scipy.stats | When passing values `(x_k, p_k)` to `stats.rv_discrete`, the only condition that is checked in `rv_sample` is whether `sum(p_k)` is one, but not whether the p_k are between zero and one
### Reproducing code example:
```
from scipy import stats
import numpy as np
custm = stats.rv_discrete(values=((1, 2, 3), (0.5, 1.2, -0.7))) # no error
```
### Scipy/Numpy/Python version information:
```
import sys, scipy, numpy; print(scipy.__version__, numpy.__version__, sys.version_info)
1.1.0 1.15.2 sys.version_info(major=3, minor=5, micro=4, releaselevel='final', serial=0)
```
| 1.0 | rv_sample accepts invalid input in scipy.stats - When passing values `(x_k, p_k)` to `stats.rv_discrete`, the only condition that is checked in `rv_sample` is whether `sum(p_k)` is one, but not whether the p_k are between zero and one
### Reproducing code example:
```
from scipy import stats
import numpy as np
custm = stats.rv_discrete(values=((1, 2, 3), (0.5, 1.2, -0.7))) # no error
```
### Scipy/Numpy/Python version information:
```
import sys, scipy, numpy; print(scipy.__version__, numpy.__version__, sys.version_info)
1.1.0 1.15.2 sys.version_info(major=3, minor=5, micro=4, releaselevel='final', serial=0)
```
| defect | rv sample accepts invalid input in scipy stats when passing values x k p k to stats rv discrete the only condition that is checked in rv sample is whether sum p k is one but not whether the p k are between zero and one reproducing code example from scipy import stats import numpy as np custm stats rv discrete values no error scipy numpy python version information import sys scipy numpy print scipy version numpy version sys version info sys version info major minor micro releaselevel final serial | 1 |
350,210 | 10,480,349,772 | IssuesEvent | 2019-09-24 07:20:02 | StrangeLoopGames/EcoIssues | https://api.github.com/repos/StrangeLoopGames/EcoIssues | opened | [master-preview] Voice chat bugs | Medium Priority | 1. When I speak I can't see microphone icon.
2. Icon to mute/unmute another player dissapeared.

| 1.0 | [master-preview] Voice chat bugs - 1. When I speak I can't see microphone icon.
2. Icon to mute/unmute another player dissapeared.

| non_defect | voice chat bugs when i speak i can t see microphone icon icon to mute unmute another player dissapeared | 0 |
9,869 | 2,616,004,943 | IssuesEvent | 2015-03-02 00:49:31 | jasonhall/bwapi | https://api.github.com/repos/jasonhall/bwapi | closed | AI Fails on second game | auto-migrated Priority-Critical Type-Defect | ```
AI will not start on second game. Problem started around revisions 420-430.
```
Original issue reported on code.google.com by `AHeinerm` on 8 Oct 2008 at 2:46 | 1.0 | AI Fails on second game - ```
AI will not start on second game. Problem started around revisions 420-430.
```
Original issue reported on code.google.com by `AHeinerm` on 8 Oct 2008 at 2:46 | defect | ai fails on second game ai will not start on second game problem started around revisions original issue reported on code google com by aheinerm on oct at | 1 |
352,749 | 10,545,801,522 | IssuesEvent | 2019-10-02 19:58:42 | aseprite/aseprite | https://api.github.com/repos/aseprite/aseprite | closed | Reduce duplicate frames into one | enhancement medium priority persistence scriptable | Feature request:
Reduce duplicate frames into one frame in output and reference them in sheet data file.
This saves memory.
### Aseprite and System version
* Aseprite 1.1.7:
| 1.0 | Reduce duplicate frames into one - Feature request:
Reduce duplicate frames into one frame in output and reference them in sheet data file.
This saves memory.
### Aseprite and System version
* Aseprite 1.1.7:
| non_defect | reduce duplicate frames into one feature request reduce duplicate frames into one frame in output and reference them in sheet data file this saves memory aseprite and system version aseprite | 0 |
53,713 | 13,262,129,548 | IssuesEvent | 2020-08-20 21:09:36 | icecube-trac/tix4 | https://api.github.com/repos/icecube-trac/tix4 | closed | [dataclasses] Rounding error in I3Time pybindings (Trac #1920) | Migrated from Trac combo core defect | The conversion from an I3Time object to a Python datetime doesn't round correctly and can create invalid datetime objects.
Example:
```text
In[1]: from icecube import dataclasses
In[2]: mjd = 57727.83222222222
In [3]: dataclasses.I3Time(mjd).date_time
Out[3]: datetime.datetime(2016, 12, 5, 19, 58, 23, 1000000)
```
Here, the datetime object has one million milliseconds, when instead, the seconds should have been incremented by one, and the milliseconds should be zero. When creating the datetime object directly in python, bounds checking would have prevented this.
Why does it matter?
The subsequent conversion to a UTC string will be invalid because the fractional seconds representation is wrong. These strings are passed around in the I3Live API and trigger further errors there.
Such behaviour is easily encountered if the times have been rounded to seconds at some point and the precision of float turns x.0 into (x-1).9999999...
The error originates here: [http://code.icecube.wisc.edu/projects/icecube/browser/IceCube/projects/dataclasses/trunk/private/pybindings/I3Time.cxx#L46 I3Time.cxx]
The nanoseconds from I3Time are rounded to milliseconds, but the overflow is not transferred to seconds, etc. A possible solution would be to round the timestamp first, and then derive the year/month/day/hours/minutes/seconds/milliseconds.
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/1920">https://code.icecube.wisc.edu/projects/icecube/ticket/1920</a>, reported by thomas.kintscherand owned by olivas</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:13:52",
"_ts": "1550067232264679",
"description": "The conversion from an I3Time object to a Python datetime doesn't round correctly and can create invalid datetime objects.\n\nExample:\n{{{\nIn[1]: from icecube import dataclasses\n\nIn[2]: mjd = 57727.83222222222\n\nIn [3]: dataclasses.I3Time(mjd).date_time\nOut[3]: datetime.datetime(2016, 12, 5, 19, 58, 23, 1000000)\n}}}\n\nHere, the datetime object has one million milliseconds, when instead, the seconds should have been incremented by one, and the milliseconds should be zero. When creating the datetime object directly in python, bounds checking would have prevented this.\n\nWhy does it matter?\nThe subsequent conversion to a UTC string will be invalid because the fractional seconds representation is wrong. These strings are passed around in the I3Live API and trigger further errors there.\nSuch behaviour is easily encountered if the times have been rounded to seconds at some point and the precision of float turns x.0 into (x-1).9999999...\n\nThe error originates here: [http://code.icecube.wisc.edu/projects/icecube/browser/IceCube/projects/dataclasses/trunk/private/pybindings/I3Time.cxx#L46 I3Time.cxx]\nThe nanoseconds from I3Time are rounded to milliseconds, but the overflow is not transferred to seconds, etc. A possible solution would be to round the timestamp first, and then derive the year/month/day/hours/minutes/seconds/milliseconds.",
"reporter": "thomas.kintscher",
"cc": "dxu",
"resolution": "fixed",
"time": "2016-12-06T10:34:31",
"component": "combo core",
"summary": "[dataclasses] Rounding error in I3Time pybindings",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "olivas",
"type": "defect"
}
```
</p>
</details>
| 1.0 | [dataclasses] Rounding error in I3Time pybindings (Trac #1920) - The conversion from an I3Time object to a Python datetime doesn't round correctly and can create invalid datetime objects.
Example:
```text
In[1]: from icecube import dataclasses
In[2]: mjd = 57727.83222222222
In [3]: dataclasses.I3Time(mjd).date_time
Out[3]: datetime.datetime(2016, 12, 5, 19, 58, 23, 1000000)
```
Here, the datetime object has one million milliseconds, when instead, the seconds should have been incremented by one, and the milliseconds should be zero. When creating the datetime object directly in python, bounds checking would have prevented this.
Why does it matter?
The subsequent conversion to a UTC string will be invalid because the fractional seconds representation is wrong. These strings are passed around in the I3Live API and trigger further errors there.
Such behaviour is easily encountered if the times have been rounded to seconds at some point and the precision of float turns x.0 into (x-1).9999999...
The error originates here: [http://code.icecube.wisc.edu/projects/icecube/browser/IceCube/projects/dataclasses/trunk/private/pybindings/I3Time.cxx#L46 I3Time.cxx]
The nanoseconds from I3Time are rounded to milliseconds, but the overflow is not transferred to seconds, etc. A possible solution would be to round the timestamp first, and then derive the year/month/day/hours/minutes/seconds/milliseconds.
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/1920">https://code.icecube.wisc.edu/projects/icecube/ticket/1920</a>, reported by thomas.kintscherand owned by olivas</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:13:52",
"_ts": "1550067232264679",
"description": "The conversion from an I3Time object to a Python datetime doesn't round correctly and can create invalid datetime objects.\n\nExample:\n{{{\nIn[1]: from icecube import dataclasses\n\nIn[2]: mjd = 57727.83222222222\n\nIn [3]: dataclasses.I3Time(mjd).date_time\nOut[3]: datetime.datetime(2016, 12, 5, 19, 58, 23, 1000000)\n}}}\n\nHere, the datetime object has one million milliseconds, when instead, the seconds should have been incremented by one, and the milliseconds should be zero. When creating the datetime object directly in python, bounds checking would have prevented this.\n\nWhy does it matter?\nThe subsequent conversion to a UTC string will be invalid because the fractional seconds representation is wrong. These strings are passed around in the I3Live API and trigger further errors there.\nSuch behaviour is easily encountered if the times have been rounded to seconds at some point and the precision of float turns x.0 into (x-1).9999999...\n\nThe error originates here: [http://code.icecube.wisc.edu/projects/icecube/browser/IceCube/projects/dataclasses/trunk/private/pybindings/I3Time.cxx#L46 I3Time.cxx]\nThe nanoseconds from I3Time are rounded to milliseconds, but the overflow is not transferred to seconds, etc. A possible solution would be to round the timestamp first, and then derive the year/month/day/hours/minutes/seconds/milliseconds.",
"reporter": "thomas.kintscher",
"cc": "dxu",
"resolution": "fixed",
"time": "2016-12-06T10:34:31",
"component": "combo core",
"summary": "[dataclasses] Rounding error in I3Time pybindings",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "olivas",
"type": "defect"
}
```
</p>
</details>
| defect | rounding error in pybindings trac the conversion from an object to a python datetime doesn t round correctly and can create invalid datetime objects example text in from icecube import dataclasses in mjd in dataclasses mjd date time out datetime datetime here the datetime object has one million milliseconds when instead the seconds should have been incremented by one and the milliseconds should be zero when creating the datetime object directly in python bounds checking would have prevented this why does it matter the subsequent conversion to a utc string will be invalid because the fractional seconds representation is wrong these strings are passed around in the api and trigger further errors there such behaviour is easily encountered if the times have been rounded to seconds at some point and the precision of float turns x into x the error originates here the nanoseconds from are rounded to milliseconds but the overflow is not transferred to seconds etc a possible solution would be to round the timestamp first and then derive the year month day hours minutes seconds milliseconds migrated from json status closed changetime ts description the conversion from an object to a python datetime doesn t round correctly and can create invalid datetime objects n nexample n nin from icecube import dataclasses n nin mjd n nin dataclasses mjd date time nout datetime datetime n n nhere the datetime object has one million milliseconds when instead the seconds should have been incremented by one and the milliseconds should be zero when creating the datetime object directly in python bounds checking would have prevented this n nwhy does it matter nthe subsequent conversion to a utc string will be invalid because the fractional seconds representation is wrong these strings are passed around in the api and trigger further errors there nsuch behaviour is easily encountered if the times have been rounded to seconds at some point and the precision of float turns x into x n nthe error originates here nthe nanoseconds from are rounded to milliseconds but the overflow is not transferred to seconds etc a possible solution would be to round the timestamp first and then derive the year month day hours minutes seconds milliseconds reporter thomas kintscher cc dxu resolution fixed time component combo core summary rounding error in pybindings priority normal keywords milestone owner olivas type defect | 1 |
449,209 | 12,965,065,297 | IssuesEvent | 2020-07-20 21:37:19 | googleinterns/step190-2020 | https://api.github.com/repos/googleinterns/step190-2020 | opened | Popup on button click that redirects the user to a voter registration site | Priority: High Type: Feature | When user clicks the TurboVote button on first page, open up a popup window that allows user to register to vote through the TurboVote API. On exit, go to the second page. | 1.0 | Popup on button click that redirects the user to a voter registration site - When user clicks the TurboVote button on first page, open up a popup window that allows user to register to vote through the TurboVote API. On exit, go to the second page. | non_defect | popup on button click that redirects the user to a voter registration site when user clicks the turbovote button on first page open up a popup window that allows user to register to vote through the turbovote api on exit go to the second page | 0 |
180,876 | 30,586,604,453 | IssuesEvent | 2023-07-21 13:50:36 | Autodesk/hig | https://api.github.com/repos/Autodesk/hig | closed | Dropdown only allows for strict comparison of options | community feature request needs api design | ## Overview
An engineer can control how options are determined to be selected to allow for more API flexibility.
## Proposed solution
Allow for a custom option comparator function to be provided to the component.
### API
Add prop to `Dropdown` named `isOptionEqual`.
```jsx
<Dropdown isOptionEqual={(a, b) => a === b} />
```
```jsx
import isEqual from "lodash.isequal";
<Dropdown isOptionEqual={isEqual} />
```
### Implementation
The comparator function should be added at the line below. However, such functionality doesn't belong in a presenter and should be hoisted.
https://github.com/Autodesk/hig/blob/development/packages/dropdown/src/presenters/renderOptions.js#L19 | 1.0 | Dropdown only allows for strict comparison of options - ## Overview
An engineer can control how options are determined to be selected to allow for more API flexibility.
## Proposed solution
Allow for a custom option comparator function to be provided to the component.
### API
Add prop to `Dropdown` named `isOptionEqual`.
```jsx
<Dropdown isOptionEqual={(a, b) => a === b} />
```
```jsx
import isEqual from "lodash.isequal";
<Dropdown isOptionEqual={isEqual} />
```
### Implementation
The comparator function should be added at the line below. However, such functionality doesn't belong in a presenter and should be hoisted.
https://github.com/Autodesk/hig/blob/development/packages/dropdown/src/presenters/renderOptions.js#L19 | non_defect | dropdown only allows for strict comparison of options overview an engineer can control how options are determined to be selected to allow for more api flexibility proposed solution allow for a custom option comparator function to be provided to the component api add prop to dropdown named isoptionequal jsx a b jsx import isequal from lodash isequal implementation the comparator function should be added at the line below however such functionality doesn t belong in a presenter and should be hoisted | 0 |
69,118 | 22,164,692,087 | IssuesEvent | 2022-06-05 02:48:40 | jezzsantos/automate | https://api.github.com/repos/jezzsantos/automate | closed | Runtime version incompatibility detection | defect-design | A toolkit that is built on a previously incompatible version of `automate`, needs to be detected and stopped from configuring an incompatible draft.
For example, a draft created with a toolkit on version 1.0.0 of `automate`, should throw an error (when being configured) if the installed version of `automate` is now 2.0.0.
The error should direct the user to upgrade the toolkit (i.e. build the toolkit) with the upgraded version of `automate`. | 1.0 | Runtime version incompatibility detection - A toolkit that is built on a previously incompatible version of `automate`, needs to be detected and stopped from configuring an incompatible draft.
For example, a draft created with a toolkit on version 1.0.0 of `automate`, should throw an error (when being configured) if the installed version of `automate` is now 2.0.0.
The error should direct the user to upgrade the toolkit (i.e. build the toolkit) with the upgraded version of `automate`. | defect | runtime version incompatibility detection a toolkit that is built on a previously incompatible version of automate needs to be detected and stopped from configuring an incompatible draft for example a draft created with a toolkit on version of automate should throw an error when being configured if the installed version of automate is now the error should direct the user to upgrade the toolkit i e build the toolkit with the upgraded version of automate | 1 |
34,563 | 7,457,240,348 | IssuesEvent | 2018-03-30 02:51:53 | kerdokullamae/test_koik_issued | https://api.github.com/repos/kerdokullamae/test_koik_issued | closed | Avalehel inglise keelele lülitumine ei tööta | C: AIS P: normal R: fixed T: defect | **Reported by koitsaarevet on 17 Feb 2014 14:19 UTC**
Avalehel UK lipp viitab URLile:
http://rahvusarhiiv.tietotest.ee/et/language_selection/en/
ja sealt tuleb veateade:
Tekkis viga
Ups, midagi läks valesti!
Server tagastas vea "500 Internal Server Error".
Lae leht uuesti või anna teada süsteemi haldajale.
Viga on ainult avalehe lingis, sest tegelikult inglise keel käivitub ja jääb ka kenasti aktiivseks, kui suvalises eestikeelse vaate URLis panna "et" asemele "en", näiteks:
http://rahvusarhiiv.tietotest.ee/en/description_unit/list/?term=mudru
Sama seis on RA testserveris. | 1.0 | Avalehel inglise keelele lülitumine ei tööta - **Reported by koitsaarevet on 17 Feb 2014 14:19 UTC**
Avalehel UK lipp viitab URLile:
http://rahvusarhiiv.tietotest.ee/et/language_selection/en/
ja sealt tuleb veateade:
Tekkis viga
Ups, midagi läks valesti!
Server tagastas vea "500 Internal Server Error".
Lae leht uuesti või anna teada süsteemi haldajale.
Viga on ainult avalehe lingis, sest tegelikult inglise keel käivitub ja jääb ka kenasti aktiivseks, kui suvalises eestikeelse vaate URLis panna "et" asemele "en", näiteks:
http://rahvusarhiiv.tietotest.ee/en/description_unit/list/?term=mudru
Sama seis on RA testserveris. | defect | avalehel inglise keelele lülitumine ei tööta reported by koitsaarevet on feb utc avalehel uk lipp viitab urlile ja sealt tuleb veateade tekkis viga ups midagi läks valesti server tagastas vea internal server error lae leht uuesti või anna teada süsteemi haldajale viga on ainult avalehe lingis sest tegelikult inglise keel käivitub ja jääb ka kenasti aktiivseks kui suvalises eestikeelse vaate urlis panna et asemele en näiteks sama seis on ra testserveris | 1 |
69,105 | 17,572,493,479 | IssuesEvent | 2021-08-15 01:12:04 | dart-lang/sdk | https://api.github.com/repos/dart-lang/sdk | closed | No publisher analyser available for language version 2.10.0 | needs-info area-build | Thank you for taking the time to file an issue!
This tracker is for issues related to:
* Analyzer
* Common Front End (CFE) and kernel
* Dart core libraries ("dart:async", "dart:io", etc.)
* Dart VM
* dart2js
* dev_compiler
Some other pieces of the Dart ecosystem are maintained elsewhere. Please
file issues in their repository:
* Dart language: https://github.com/dart-lang/language
* Dart website: https://github.com/dart-lang/site-www
* Flutter: https://github.com/flutter/flutter
* Linter: https://github.com/dart-lang/linter
* dartfmt: https://github.com/dart-lang/dart_style
If you aren't sure, file the issue here and we'll find the right home for it.
In your issue, please include:
* Dart SDK Version (`dart --version`)
* Whether you are using Windows, MacOSX, or Linux (if applicable)
* Whether you are using Chrome, Safari, Firefox, Edge (if applicable)
Missing some or all of the above might make the issue take longer or be
impossible to act on.
If you simply have a question, consider starting with Stack Overflow:
https://stackoverflow.com/questions/tagged/dart
For a real-time response, consider our Gitter channel:
https://gitter.im/dart-lang/sdk
| 1.0 | No publisher analyser available for language version 2.10.0 - Thank you for taking the time to file an issue!
This tracker is for issues related to:
* Analyzer
* Common Front End (CFE) and kernel
* Dart core libraries ("dart:async", "dart:io", etc.)
* Dart VM
* dart2js
* dev_compiler
Some other pieces of the Dart ecosystem are maintained elsewhere. Please
file issues in their repository:
* Dart language: https://github.com/dart-lang/language
* Dart website: https://github.com/dart-lang/site-www
* Flutter: https://github.com/flutter/flutter
* Linter: https://github.com/dart-lang/linter
* dartfmt: https://github.com/dart-lang/dart_style
If you aren't sure, file the issue here and we'll find the right home for it.
In your issue, please include:
* Dart SDK Version (`dart --version`)
* Whether you are using Windows, MacOSX, or Linux (if applicable)
* Whether you are using Chrome, Safari, Firefox, Edge (if applicable)
Missing some or all of the above might make the issue take longer or be
impossible to act on.
If you simply have a question, consider starting with Stack Overflow:
https://stackoverflow.com/questions/tagged/dart
For a real-time response, consider our Gitter channel:
https://gitter.im/dart-lang/sdk
| non_defect | no publisher analyser available for language version thank you for taking the time to file an issue this tracker is for issues related to analyzer common front end cfe and kernel dart core libraries dart async dart io etc dart vm dev compiler some other pieces of the dart ecosystem are maintained elsewhere please file issues in their repository dart language dart website flutter linter dartfmt if you aren t sure file the issue here and we ll find the right home for it in your issue please include dart sdk version dart version whether you are using windows macosx or linux if applicable whether you are using chrome safari firefox edge if applicable missing some or all of the above might make the issue take longer or be impossible to act on if you simply have a question consider starting with stack overflow for a real time response consider our gitter channel | 0 |
213,686 | 24,016,305,226 | IssuesEvent | 2022-09-15 01:16:42 | Whizkevina/portfolio | https://api.github.com/repos/Whizkevina/portfolio | opened | WS-2020-0042 (High) detected in acorn-5.7.4.tgz | security vulnerability | ## WS-2020-0042 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>acorn-5.7.4.tgz</b></p></summary>
<p>ECMAScript parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/acorn/-/acorn-5.7.4.tgz">https://registry.npmjs.org/acorn/-/acorn-5.7.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/jsdom/node_modules/acorn/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.0.1.tgz (Root Library)
- jest-24.7.1.tgz
- jest-cli-24.9.0.tgz
- jest-config-24.9.0.tgz
- jest-environment-jsdom-24.9.0.tgz
- jsdom-11.12.0.tgz
- :x: **acorn-5.7.4.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
acorn is vulnerable to REGEX DoS. A regex of the form /[x-\ud800]/u causes the parser to enter an infinite loop. attackers may leverage the vulnerability leading to a Denial of Service since the string is not valid UTF16 and it results in it being sanitized before reaching the parser.
<p>Publish Date: 2020-03-01
<p>URL: <a href=https://github.com/acornjs/acorn/commit/b5c17877ac0511e31579ea31e7650ba1a5871e51>WS-2020-0042</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1488">https://www.npmjs.com/advisories/1488</a></p>
<p>Release Date: 2020-03-01</p>
<p>Fix Resolution (acorn): 6.4.1</p>
<p>Direct dependency fix Resolution (react-scripts): 3.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2020-0042 (High) detected in acorn-5.7.4.tgz - ## WS-2020-0042 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>acorn-5.7.4.tgz</b></p></summary>
<p>ECMAScript parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/acorn/-/acorn-5.7.4.tgz">https://registry.npmjs.org/acorn/-/acorn-5.7.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/jsdom/node_modules/acorn/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.0.1.tgz (Root Library)
- jest-24.7.1.tgz
- jest-cli-24.9.0.tgz
- jest-config-24.9.0.tgz
- jest-environment-jsdom-24.9.0.tgz
- jsdom-11.12.0.tgz
- :x: **acorn-5.7.4.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
acorn is vulnerable to REGEX DoS. A regex of the form /[x-\ud800]/u causes the parser to enter an infinite loop. attackers may leverage the vulnerability leading to a Denial of Service since the string is not valid UTF16 and it results in it being sanitized before reaching the parser.
<p>Publish Date: 2020-03-01
<p>URL: <a href=https://github.com/acornjs/acorn/commit/b5c17877ac0511e31579ea31e7650ba1a5871e51>WS-2020-0042</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1488">https://www.npmjs.com/advisories/1488</a></p>
<p>Release Date: 2020-03-01</p>
<p>Fix Resolution (acorn): 6.4.1</p>
<p>Direct dependency fix Resolution (react-scripts): 3.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_defect | ws high detected in acorn tgz ws high severity vulnerability vulnerable library acorn tgz ecmascript parser library home page a href path to dependency file package json path to vulnerable library node modules jsdom node modules acorn package json dependency hierarchy react scripts tgz root library jest tgz jest cli tgz jest config tgz jest environment jsdom tgz jsdom tgz x acorn tgz vulnerable library vulnerability details acorn is vulnerable to regex dos a regex of the form u causes the parser to enter an infinite loop attackers may leverage the vulnerability leading to a denial of service since the string is not valid and it results in it being sanitized before reaching the parser publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution acorn direct dependency fix resolution react scripts step up your open source security game with mend | 0 |
521,656 | 15,113,246,964 | IssuesEvent | 2021-02-08 23:17:09 | sonia-auv/octopus-telemetry | https://api.github.com/repos/sonia-auv/octopus-telemetry | closed | Ros-bridge test data/replay bag | Priority: High Type: Feature | **Warning :** Before creating an issue or task, make sure that it does not already exists in the [issue tracker](../). Thank you.
## Context
Installer ROS-bridge et essayer de simuler du data
## Changes
<!-- Give a brief description of the components that need to change and how -->
## Comments
<!-- Add further comments if needed -->
| 1.0 | Ros-bridge test data/replay bag - **Warning :** Before creating an issue or task, make sure that it does not already exists in the [issue tracker](../). Thank you.
## Context
Installer ROS-bridge et essayer de simuler du data
## Changes
<!-- Give a brief description of the components that need to change and how -->
## Comments
<!-- Add further comments if needed -->
| non_defect | ros bridge test data replay bag warning before creating an issue or task make sure that it does not already exists in the thank you context installer ros bridge et essayer de simuler du data changes comments | 0 |
116,853 | 17,392,511,074 | IssuesEvent | 2021-08-02 09:14:31 | SmartBear/ready-jira-plugin | https://api.github.com/repos/SmartBear/ready-jira-plugin | closed | CVE-2021-27568 (High) detected in json-smart-2.3.jar - autoclosed | security vulnerability | ## CVE-2021-27568 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>json-smart-2.3.jar</b></p></summary>
<p>JSON (JavaScript Object Notation) is a lightweight data-interchange format. It is easy for humans to read and write. It is easy for machines to parse and generate. It is based on a subset of the JavaScript Programming Language, Standard ECMA-262 3rd Edition - December 1999. JSON is a text format that is completely language independent but uses conventions that are familiar to programmers of the C-family of languages, including C, C++, C#, Java, JavaScript, Perl, Python, and many others. These properties make JSON an ideal data-interchange language.</p>
<p>Library home page: <a href="http://www.minidev.net/">http://www.minidev.net/</a></p>
<p>Path to dependency file: ready-jira-plugin/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/net/minidev/json-smart/2.3/json-smart-2.3.jar</p>
<p>
Dependency Hierarchy:
- ready-api-soapui-ng-3.5.0.jar (Root Library)
- ready-api-security-3.5.0.jar
- ready-api-core-3.5.0.jar
- json-path-2.4.0-fixed.jar
- :x: **json-smart-2.3.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in netplex json-smart-v1 through 2015-10-23 and json-smart-v2 through 2.4. An exception is thrown from a function, but it is not caught, as demonstrated by NumberFormatException. When it is not caught, it may cause programs using the library to crash or expose sensitive information.
<p>Publish Date: 2021-02-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27568>CVE-2021-27568</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/netplex/json-smart-v1/issues/7">https://github.com/netplex/json-smart-v1/issues/7</a></p>
<p>Release Date: 2021-02-23</p>
<p>Fix Resolution: net.minidev:json-smart-mini:1.3.2, net.minidev:json-smart:1.3.2, 2.4.2, net.minidev:json-smart-action:2.4.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"net.minidev","packageName":"json-smart","packageVersion":"2.3","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"com.smartbear:ready-api-soapui-ng:3.5.0;com.smartbear:ready-api-security:3.5.0;com.smartbear:ready-api-core:3.5.0;com.jayway.jsonpath:json-path:2.4.0-fixed;net.minidev:json-smart:2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"net.minidev:json-smart-mini:1.3.2, net.minidev:json-smart:1.3.2, 2.4.2, net.minidev:json-smart-action:2.4.2"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-27568","vulnerabilityDetails":"An issue was discovered in netplex json-smart-v1 through 2015-10-23 and json-smart-v2 through 2.4. An exception is thrown from a function, but it is not caught, as demonstrated by NumberFormatException. When it is not caught, it may cause programs using the library to crash or expose sensitive information.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27568","cvss3Severity":"high","cvss3Score":"9.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-27568 (High) detected in json-smart-2.3.jar - autoclosed - ## CVE-2021-27568 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>json-smart-2.3.jar</b></p></summary>
<p>JSON (JavaScript Object Notation) is a lightweight data-interchange format. It is easy for humans to read and write. It is easy for machines to parse and generate. It is based on a subset of the JavaScript Programming Language, Standard ECMA-262 3rd Edition - December 1999. JSON is a text format that is completely language independent but uses conventions that are familiar to programmers of the C-family of languages, including C, C++, C#, Java, JavaScript, Perl, Python, and many others. These properties make JSON an ideal data-interchange language.</p>
<p>Library home page: <a href="http://www.minidev.net/">http://www.minidev.net/</a></p>
<p>Path to dependency file: ready-jira-plugin/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/net/minidev/json-smart/2.3/json-smart-2.3.jar</p>
<p>
Dependency Hierarchy:
- ready-api-soapui-ng-3.5.0.jar (Root Library)
- ready-api-security-3.5.0.jar
- ready-api-core-3.5.0.jar
- json-path-2.4.0-fixed.jar
- :x: **json-smart-2.3.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in netplex json-smart-v1 through 2015-10-23 and json-smart-v2 through 2.4. An exception is thrown from a function, but it is not caught, as demonstrated by NumberFormatException. When it is not caught, it may cause programs using the library to crash or expose sensitive information.
<p>Publish Date: 2021-02-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27568>CVE-2021-27568</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/netplex/json-smart-v1/issues/7">https://github.com/netplex/json-smart-v1/issues/7</a></p>
<p>Release Date: 2021-02-23</p>
<p>Fix Resolution: net.minidev:json-smart-mini:1.3.2, net.minidev:json-smart:1.3.2, 2.4.2, net.minidev:json-smart-action:2.4.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"net.minidev","packageName":"json-smart","packageVersion":"2.3","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"com.smartbear:ready-api-soapui-ng:3.5.0;com.smartbear:ready-api-security:3.5.0;com.smartbear:ready-api-core:3.5.0;com.jayway.jsonpath:json-path:2.4.0-fixed;net.minidev:json-smart:2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"net.minidev:json-smart-mini:1.3.2, net.minidev:json-smart:1.3.2, 2.4.2, net.minidev:json-smart-action:2.4.2"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-27568","vulnerabilityDetails":"An issue was discovered in netplex json-smart-v1 through 2015-10-23 and json-smart-v2 through 2.4. An exception is thrown from a function, but it is not caught, as demonstrated by NumberFormatException. When it is not caught, it may cause programs using the library to crash or expose sensitive information.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27568","cvss3Severity":"high","cvss3Score":"9.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_defect | cve high detected in json smart jar autoclosed cve high severity vulnerability vulnerable library json smart jar json javascript object notation is a lightweight data interchange format it is easy for humans to read and write it is easy for machines to parse and generate it is based on a subset of the javascript programming language standard ecma edition december json is a text format that is completely language independent but uses conventions that are familiar to programmers of the c family of languages including c c c java javascript perl python and many others these properties make json an ideal data interchange language library home page a href path to dependency file ready jira plugin pom xml path to vulnerable library home wss scanner repository net minidev json smart json smart jar dependency hierarchy ready api soapui ng jar root library ready api security jar ready api core jar json path fixed jar x json smart jar vulnerable library found in base branch master vulnerability details an issue was discovered in netplex json smart through and json smart through an exception is thrown from a function but it is not caught as demonstrated by numberformatexception when it is not caught it may cause programs using the library to crash or expose sensitive information publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution net minidev json smart mini net minidev json smart net minidev json smart action isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree com smartbear ready api soapui ng com smartbear ready api security com smartbear ready api core com jayway jsonpath json path fixed net minidev json smart isminimumfixversionavailable true minimumfixversion net minidev json smart mini net minidev json smart net minidev json smart action basebranches vulnerabilityidentifier cve vulnerabilitydetails an issue was discovered in netplex json smart through and json smart through an exception is thrown from a function but it is not caught as demonstrated by numberformatexception when it is not caught it may cause programs using the library to crash or expose sensitive information vulnerabilityurl | 0 |
31,625 | 7,430,568,509 | IssuesEvent | 2018-03-25 03:37:46 | datasnakes/OrthoEvolution | https://api.github.com/repos/datasnakes/OrthoEvolution | closed | Combine data_management and the Luigi class | Code Style Improvement Discussion High Priority | ##### What are you trying to accomplish?
The Pipeline module is great. Whenever #38 is finished, the functionality in Manager/data_management.py needs to be used/moved in the Pipeline module.
##### What is the issue?
The workflow is awkward as it stands.
Will help with #32. | 1.0 | Combine data_management and the Luigi class - ##### What are you trying to accomplish?
The Pipeline module is great. Whenever #38 is finished, the functionality in Manager/data_management.py needs to be used/moved in the Pipeline module.
##### What is the issue?
The workflow is awkward as it stands.
Will help with #32. | non_defect | combine data management and the luigi class what are you trying to accomplish the pipeline module is great whenever is finished the functionality in manager data management py needs to be used moved in the pipeline module what is the issue the workflow is awkward as it stands will help with | 0 |
825,093 | 31,271,846,508 | IssuesEvent | 2023-08-22 01:06:26 | QUT-Digital-Observatory/australian_digital_observatory_site | https://api.github.com/repos/QUT-Digital-Observatory/australian_digital_observatory_site | closed | [CONTENT UPDATE] Update Twitter platform fact sheet | high priority | https://www.digitalobservatory.net.au/factsheets/platform-factsheet-twitter/
Twitter is now X, and there are new API tiers. The fact sheet needs updating accordingly. It should also include a link to this really helpful article: https://www.rmit.edu.au/news/crosscheck/navigating-x-formerly-twitter | 1.0 | [CONTENT UPDATE] Update Twitter platform fact sheet - https://www.digitalobservatory.net.au/factsheets/platform-factsheet-twitter/
Twitter is now X, and there are new API tiers. The fact sheet needs updating accordingly. It should also include a link to this really helpful article: https://www.rmit.edu.au/news/crosscheck/navigating-x-formerly-twitter | non_defect | update twitter platform fact sheet twitter is now x and there are new api tiers the fact sheet needs updating accordingly it should also include a link to this really helpful article | 0 |
36,816 | 8,142,511,666 | IssuesEvent | 2018-08-21 07:52:39 | ShaikASK/Testing | https://api.github.com/repos/ShaikASK/Testing | opened | Payroll Method selection form : Text is getting overlapped when the candidate is planing to sign the PDF document | Defect P3 Payroll Package form | Steps To Replicate :
1. Launch the URL
2. Sign in as Candidate credentials
3. Click on "Get Started" button
4. Sign the "Offer Letter"
5. Fill the common details form
6. Submit the form
7. Navigate to BGV form fill the for and click on next button
8. Navigate to 'Payroll" form and select "Direct Deposit" radio option and click on next
9. Navigate to 'EEO" form fill the EEO for click on next
10. Navigate to "Dashboard" screen
11. Check the payroll form present on the "Dashboard" screen
Experienced Behavior : Observed that where ever there is letter "L / l " the text is being overlapped , Attaching screen shot for more reference.

| 1.0 | Payroll Method selection form : Text is getting overlapped when the candidate is planing to sign the PDF document - Steps To Replicate :
1. Launch the URL
2. Sign in as Candidate credentials
3. Click on "Get Started" button
4. Sign the "Offer Letter"
5. Fill the common details form
6. Submit the form
7. Navigate to BGV form fill the for and click on next button
8. Navigate to 'Payroll" form and select "Direct Deposit" radio option and click on next
9. Navigate to 'EEO" form fill the EEO for click on next
10. Navigate to "Dashboard" screen
11. Check the payroll form present on the "Dashboard" screen
Experienced Behavior : Observed that where ever there is letter "L / l " the text is being overlapped , Attaching screen shot for more reference.

| defect | payroll method selection form text is getting overlapped when the candidate is planing to sign the pdf document steps to replicate launch the url sign in as candidate credentials click on get started button sign the offer letter fill the common details form submit the form navigate to bgv form fill the for and click on next button navigate to payroll form and select direct deposit radio option and click on next navigate to eeo form fill the eeo for click on next navigate to dashboard screen check the payroll form present on the dashboard screen experienced behavior observed that where ever there is letter l l the text is being overlapped attaching screen shot for more reference | 1 |
16,379 | 2,889,859,453 | IssuesEvent | 2015-06-13 20:40:50 | damonkohler/android-scripting | https://api.github.com/repos/damonkohler/android-scripting | closed | Remove unnecessary files from Lua distribution | auto-migrated Priority-Medium Type-Defect | ```
liblua.a is copied to the device as part of the installation and doesn't
need to be.
```
Original issue reported on code.google.com by `damonkoh...@gmail.com` on 10 Mar 2010 at 4:44 | 1.0 | Remove unnecessary files from Lua distribution - ```
liblua.a is copied to the device as part of the installation and doesn't
need to be.
```
Original issue reported on code.google.com by `damonkoh...@gmail.com` on 10 Mar 2010 at 4:44 | defect | remove unnecessary files from lua distribution liblua a is copied to the device as part of the installation and doesn t need to be original issue reported on code google com by damonkoh gmail com on mar at | 1 |
29,483 | 5,697,659,197 | IssuesEvent | 2017-04-16 23:59:40 | i2p/i2p.i2p-bote | https://api.github.com/repos/i2p/i2p.i2p-bote | closed | i2p.bote.folder.Folder : Can't create a FolderElement from file (Trac #937) | apps/plugins defect Migrated from Trac str4d | ERROR [RelayPktSndr] i2p.bote.folder.Folder : Can't create a FolderElement from file: /var/lib/i2p/i2p-config/i2pbote/relay_pkt/[REDACTED].pkt (file size=0)
java.lang.NullPointerException
at i2p.bote.folder.RelayPacketFolder.createFolderElement(RelayPacketFolder.java:79)
at i2p.bote.folder.RelayPacketFolder.createFolderElement(RelayPacketFolder.java:39)
at i2p.bote.folder.Folder$3.findNextElement(Folder.java:164)
at i2p.bote.folder.Folder$3.next(Folder.java:145)
at i2p.bote.folder.PacketFolder$1.next(PacketFolder.java:106)
at i2p.bote.folder.PacketFolder$1.next(PacketFolder.java:90)
at i2p.bote.service.RelayPacketSender.run(RelayPacketSender.java:69)
2 times this error
Migrated from https://trac.i2p2.de/ticket/937
```json
{
"status": "closed",
"changetime": "2015-07-22T21:17:05",
"description": "ERROR [RelayPktSndr] i2p.bote.folder.Folder : Can't create a FolderElement from file: /var/lib/i2p/i2p-config/i2pbote/relay_pkt/[REDACTED].pkt (file size=0)\n java.lang.NullPointerException\n at i2p.bote.folder.RelayPacketFolder.createFolderElement(RelayPacketFolder.java:79)\n at i2p.bote.folder.RelayPacketFolder.createFolderElement(RelayPacketFolder.java:39)\n at i2p.bote.folder.Folder$3.findNextElement(Folder.java:164)\n at i2p.bote.folder.Folder$3.next(Folder.java:145)\n at i2p.bote.folder.PacketFolder$1.next(PacketFolder.java:106)\n at i2p.bote.folder.PacketFolder$1.next(PacketFolder.java:90)\n at i2p.bote.service.RelayPacketSender.run(RelayPacketSender.java:69)\n\n2 times this error",
"reporter": "guest",
"cc": "",
"resolution": "fixed",
"_ts": "1437599825195621",
"component": "apps/plugins",
"summary": "i2p.bote.folder.Folder : Can't create a FolderElement from file",
"priority": "minor",
"keywords": "I2P-Bote",
"version": "0.9.5",
"parents": "",
"time": "2013-05-26T19:44:18",
"milestone": "0.9.21",
"owner": "str4d",
"type": "defect"
}
```
| 1.0 | i2p.bote.folder.Folder : Can't create a FolderElement from file (Trac #937) - ERROR [RelayPktSndr] i2p.bote.folder.Folder : Can't create a FolderElement from file: /var/lib/i2p/i2p-config/i2pbote/relay_pkt/[REDACTED].pkt (file size=0)
java.lang.NullPointerException
at i2p.bote.folder.RelayPacketFolder.createFolderElement(RelayPacketFolder.java:79)
at i2p.bote.folder.RelayPacketFolder.createFolderElement(RelayPacketFolder.java:39)
at i2p.bote.folder.Folder$3.findNextElement(Folder.java:164)
at i2p.bote.folder.Folder$3.next(Folder.java:145)
at i2p.bote.folder.PacketFolder$1.next(PacketFolder.java:106)
at i2p.bote.folder.PacketFolder$1.next(PacketFolder.java:90)
at i2p.bote.service.RelayPacketSender.run(RelayPacketSender.java:69)
2 times this error
Migrated from https://trac.i2p2.de/ticket/937
```json
{
"status": "closed",
"changetime": "2015-07-22T21:17:05",
"description": "ERROR [RelayPktSndr] i2p.bote.folder.Folder : Can't create a FolderElement from file: /var/lib/i2p/i2p-config/i2pbote/relay_pkt/[REDACTED].pkt (file size=0)\n java.lang.NullPointerException\n at i2p.bote.folder.RelayPacketFolder.createFolderElement(RelayPacketFolder.java:79)\n at i2p.bote.folder.RelayPacketFolder.createFolderElement(RelayPacketFolder.java:39)\n at i2p.bote.folder.Folder$3.findNextElement(Folder.java:164)\n at i2p.bote.folder.Folder$3.next(Folder.java:145)\n at i2p.bote.folder.PacketFolder$1.next(PacketFolder.java:106)\n at i2p.bote.folder.PacketFolder$1.next(PacketFolder.java:90)\n at i2p.bote.service.RelayPacketSender.run(RelayPacketSender.java:69)\n\n2 times this error",
"reporter": "guest",
"cc": "",
"resolution": "fixed",
"_ts": "1437599825195621",
"component": "apps/plugins",
"summary": "i2p.bote.folder.Folder : Can't create a FolderElement from file",
"priority": "minor",
"keywords": "I2P-Bote",
"version": "0.9.5",
"parents": "",
"time": "2013-05-26T19:44:18",
"milestone": "0.9.21",
"owner": "str4d",
"type": "defect"
}
```
| defect | bote folder folder can t create a folderelement from file trac error bote folder folder can t create a folderelement from file var lib config relay pkt pkt file size java lang nullpointerexception at bote folder relaypacketfolder createfolderelement relaypacketfolder java at bote folder relaypacketfolder createfolderelement relaypacketfolder java at bote folder folder findnextelement folder java at bote folder folder next folder java at bote folder packetfolder next packetfolder java at bote folder packetfolder next packetfolder java at bote service relaypacketsender run relaypacketsender java times this error migrated from json status closed changetime description error bote folder folder can t create a folderelement from file var lib config relay pkt pkt file size n java lang nullpointerexception n at bote folder relaypacketfolder createfolderelement relaypacketfolder java n at bote folder relaypacketfolder createfolderelement relaypacketfolder java n at bote folder folder findnextelement folder java n at bote folder folder next folder java n at bote folder packetfolder next packetfolder java n at bote folder packetfolder next packetfolder java n at bote service relaypacketsender run relaypacketsender java n times this error reporter guest cc resolution fixed ts component apps plugins summary bote folder folder can t create a folderelement from file priority minor keywords bote version parents time milestone owner type defect | 1 |
439,216 | 30,685,060,219 | IssuesEvent | 2023-07-26 11:47:34 | SAP/terraform-provider-btp | https://api.github.com/repos/SAP/terraform-provider-btp | closed | [DOCU] Impact of Firewall Setups | documentation | To allow a smooth user experience when using the Terraform provider especially for new customers that have no experience with Terraform *per se* we should:
- [x] Evaluate if typical firewall setups in a company can cause issues when setting up the Terraform provider
- [x] If issues occur we need to document and give advice how to deal with them as part of the official documentation (arrea: provider setup) | 1.0 | [DOCU] Impact of Firewall Setups - To allow a smooth user experience when using the Terraform provider especially for new customers that have no experience with Terraform *per se* we should:
- [x] Evaluate if typical firewall setups in a company can cause issues when setting up the Terraform provider
- [x] If issues occur we need to document and give advice how to deal with them as part of the official documentation (arrea: provider setup) | non_defect | impact of firewall setups to allow a smooth user experience when using the terraform provider especially for new customers that have no experience with terraform per se we should evaluate if typical firewall setups in a company can cause issues when setting up the terraform provider if issues occur we need to document and give advice how to deal with them as part of the official documentation arrea provider setup | 0 |
55 | 2,499,487,963 | IssuesEvent | 2015-01-08 01:05:04 | ophrescue/RescueRails | https://api.github.com/repos/ophrescue/RescueRails | closed | Unable to Link Dogs | Defect in progress Priority | Defect verified, and probably introduced in last night's release somehow.
Linking dogs to Adoption Applications doesn't work correctly. | 1.0 | Unable to Link Dogs - Defect verified, and probably introduced in last night's release somehow.
Linking dogs to Adoption Applications doesn't work correctly. | defect | unable to link dogs defect verified and probably introduced in last night s release somehow linking dogs to adoption applications doesn t work correctly | 1 |
72,780 | 24,287,285,179 | IssuesEvent | 2022-09-29 00:13:17 | SeleniumHQ/selenium | https://api.github.com/repos/SeleniumHQ/selenium | closed | [🐛 Bug]: When click element in an iframe with padding-left or padding-top , the coordinate of the click is wrong. | D-IE I-defect | ### What happened?
When click element in an iframe with padding-left or padding-top , the coordinate of the click is wrong.
But I solved the problem on my own in my local environment, and I will show my code below..
I found that in Element.cpp, bool Element::AppendFrameDetails(std::vector<LocationInfo>\* frame_locations); . The frame location's calculation is forget to do the addtion of the padding of the iframe...
I added a piece of code after ' frame_location.y += top_border_width ' and solved the problem...
```C++
{
CComPtr<IHTMLWindow7> style_window;
hr = parent_window->QueryInterface<IHTMLWindow7>(&style_window);
if (SUCCEEDED(hr) && style_window) {
CComPtr<IHTMLDOMNode> node;
hr = frame_element->QueryInterface<IHTMLDOMNode>(&node);
if(SUCCEEDED(hr) && node){
CComPtr<IHTMLCSSStyleDeclaration> styleDec;
hr = style_window->getComputedStyle(node, NULL, &styleDec);
if(SUCCEEDED(hr) && styleDec){
VARIANT varPaddingLeft, varPaddingTop;
styleDec->get_paddingLeft(&varPaddingLeft);
styleDec->get_paddingTop(&varPaddingTop);
long paddingLeft = parseVarPadding(&varPaddingLeft);
long paddingTop = parseVarPadding(&varPaddingTop);
frame_location.x += paddingLeft;
frame_location.y += paddingTop;
}
}
}
}
```
```C++
long parseVarPadding(VARIANT* var){
if(var->bstrVal){
std::wstring bstr_value = var->bstrVal;
std::string pStr = StringUtilities:ToString(bstr_value);
if (pStr.length() > 0){
long result = 0;
int idx = 0;
while(idx < pStr.length() && (pStr[idx] < '0' || pStr[idx] > '9')) idx++;
while(idx < pStr.length() && (pStr[idx] >='0' && pStr[idx] <= '9')){
result = result * 10 + (pStr[idx] - '0');
idx++;
}
return result;
}
}
return 0;
}
```
### How can we reproduce the issue?
```shell
I have two html file.
aaa.html (iframe content):
<html>
<head>
</head>
<body>
<script>
function ccc(){
console.log("hhh");
console.log(document.getElementById("zzz").getBoundingClientRect());
}
</script>
<script type="text/javascript">
var allItems = document.querySelectorAll("*");
for(var i in allItems){
var elem = allItems[i];
elem.addEventListener("click", function(e) { console.log(e, "capture"); }, true);
}
</script>
<div style="float: left;">
<input style="width: 300px;"/>
<img style="margin-left: 30px; cursor: pointer;" id="zzz" src="q.PNG" onclick="ccc();"/>
</div>
</body>
</html>
bbb.html (main html file):
```html
<html>
<head>
</head>
<body>
<iframe id="iii" style="padding-left: 50px;" src="aaa.html" width=1000 height=700></iframe>
</body>
</html>
```
Selenium Java code:
```java
WebDriver driver = new InternetExplorerDriver();
driver.switchTo().frame(0);
driver.findElement(By.id("zzz")).click();
```
```
### Relevant log output
```shell
Console output infers that the coordinate of the click by selenium is (370, 58). (All elements in iframe have capture event listeners attached, so I can get native coordinate relative to the sub page)
but my boundingClientRect of the img element is (x: 342, y: 8, width: 156, height: 100, top: 8). So, the click coordinate suppose to be (420, 58).
Why is the actual click coordinate offset to the left by 50px, exactly the padding-left value of the iframe. I think the reason is when IEWebDriver calculate the click coordinate relative to the browser viewport, the IEWebDriver forget to add the padding value ...... But luckily, I found that the IEWebDriver do the addition of border width value of the iframe ...
```
### Operating System
Windows 10
### Selenium version
Java 4.4.0
### What are the browser(s) and version(s) where you see this issue?
IE 11
### What are the browser driver(s) and version(s) where you see this issue?
IEDriverServer)Win32_4.4.0.exe
### Are you using Selenium Grid?
4.4.0 | 1.0 | [🐛 Bug]: When click element in an iframe with padding-left or padding-top , the coordinate of the click is wrong. - ### What happened?
When click element in an iframe with padding-left or padding-top , the coordinate of the click is wrong.
But I solved the problem on my own in my local environment, and I will show my code below..
I found that in Element.cpp, bool Element::AppendFrameDetails(std::vector<LocationInfo>\* frame_locations); . The frame location's calculation is forget to do the addtion of the padding of the iframe...
I added a piece of code after ' frame_location.y += top_border_width ' and solved the problem...
```C++
{
CComPtr<IHTMLWindow7> style_window;
hr = parent_window->QueryInterface<IHTMLWindow7>(&style_window);
if (SUCCEEDED(hr) && style_window) {
CComPtr<IHTMLDOMNode> node;
hr = frame_element->QueryInterface<IHTMLDOMNode>(&node);
if(SUCCEEDED(hr) && node){
CComPtr<IHTMLCSSStyleDeclaration> styleDec;
hr = style_window->getComputedStyle(node, NULL, &styleDec);
if(SUCCEEDED(hr) && styleDec){
VARIANT varPaddingLeft, varPaddingTop;
styleDec->get_paddingLeft(&varPaddingLeft);
styleDec->get_paddingTop(&varPaddingTop);
long paddingLeft = parseVarPadding(&varPaddingLeft);
long paddingTop = parseVarPadding(&varPaddingTop);
frame_location.x += paddingLeft;
frame_location.y += paddingTop;
}
}
}
}
```
```C++
long parseVarPadding(VARIANT* var){
if(var->bstrVal){
std::wstring bstr_value = var->bstrVal;
std::string pStr = StringUtilities:ToString(bstr_value);
if (pStr.length() > 0){
long result = 0;
int idx = 0;
while(idx < pStr.length() && (pStr[idx] < '0' || pStr[idx] > '9')) idx++;
while(idx < pStr.length() && (pStr[idx] >='0' && pStr[idx] <= '9')){
result = result * 10 + (pStr[idx] - '0');
idx++;
}
return result;
}
}
return 0;
}
```
### How can we reproduce the issue?
```shell
I have two html file.
aaa.html (iframe content):
<html>
<head>
</head>
<body>
<script>
function ccc(){
console.log("hhh");
console.log(document.getElementById("zzz").getBoundingClientRect());
}
</script>
<script type="text/javascript">
var allItems = document.querySelectorAll("*");
for(var i in allItems){
var elem = allItems[i];
elem.addEventListener("click", function(e) { console.log(e, "capture"); }, true);
}
</script>
<div style="float: left;">
<input style="width: 300px;"/>
<img style="margin-left: 30px; cursor: pointer;" id="zzz" src="q.PNG" onclick="ccc();"/>
</div>
</body>
</html>
bbb.html (main html file):
```html
<html>
<head>
</head>
<body>
<iframe id="iii" style="padding-left: 50px;" src="aaa.html" width=1000 height=700></iframe>
</body>
</html>
```
Selenium Java code:
```java
WebDriver driver = new InternetExplorerDriver();
driver.switchTo().frame(0);
driver.findElement(By.id("zzz")).click();
```
```
### Relevant log output
```shell
Console output infers that the coordinate of the click by selenium is (370, 58). (All elements in iframe have capture event listeners attached, so I can get native coordinate relative to the sub page)
but my boundingClientRect of the img element is (x: 342, y: 8, width: 156, height: 100, top: 8). So, the click coordinate suppose to be (420, 58).
Why is the actual click coordinate offset to the left by 50px, exactly the padding-left value of the iframe. I think the reason is when IEWebDriver calculate the click coordinate relative to the browser viewport, the IEWebDriver forget to add the padding value ...... But luckily, I found that the IEWebDriver do the addition of border width value of the iframe ...
```
### Operating System
Windows 10
### Selenium version
Java 4.4.0
### What are the browser(s) and version(s) where you see this issue?
IE 11
### What are the browser driver(s) and version(s) where you see this issue?
IEDriverServer)Win32_4.4.0.exe
### Are you using Selenium Grid?
4.4.0 | defect | when click element in an iframe with padding left or padding top the coordinate of the click is wrong what happened when click element in an iframe with padding left or padding top the coordinate of the click is wrong but i solved the problem on my own in my local environment and i will show my code below i found that in element cpp bool element appendframedetails std vector frame locations the frame location s calculation is forget to do the addtion of the padding of the iframe i added a piece of code after frame location y top border width and solved the problem c ccomptr style window hr parent window queryinterface style window if succeeded hr style window ccomptr node hr frame element queryinterface node if succeeded hr node ccomptr styledec hr style window getcomputedstyle node null styledec if succeeded hr styledec variant varpaddingleft varpaddingtop styledec get paddingleft varpaddingleft styledec get paddingtop varpaddingtop long paddingleft parsevarpadding varpaddingleft long paddingtop parsevarpadding varpaddingtop frame location x paddingleft frame location y paddingtop c long parsevarpadding variant var if var bstrval std wstring bstr value var bstrval std string pstr stringutilities tostring bstr value if pstr length long result int idx while idx idx while idx pstr result result pstr idx return result return how can we reproduce the issue shell i have two html file aaa html iframe content function ccc console log hhh console log document getelementbyid zzz getboundingclientrect var allitems document queryselectorall for var i in allitems var elem allitems elem addeventlistener click function e console log e capture true bbb html main html file html selenium java code java webdriver driver new internetexplorerdriver driver switchto frame driver findelement by id zzz click relevant log output shell console output infers that the coordinate of the click by selenium is all elements in iframe have capture event listeners attached so i can get native coordinate relative to the sub page but my boundingclientrect of the img element is x y width height top so the click coordinate suppose to be why is the actual click coordinate offset to the left by exactly the padding left value of the iframe i think the reason is when iewebdriver calculate the click coordinate relative to the browser viewport the iewebdriver forget to add the padding value but luckily i found that the iewebdriver do the addition of border width value of the iframe operating system windows selenium version java what are the browser s and version s where you see this issue ie what are the browser driver s and version s where you see this issue iedriverserver exe are you using selenium grid | 1 |
76,890 | 26,657,703,576 | IssuesEvent | 2023-01-25 18:11:44 | dkfans/keeperfx | https://api.github.com/repos/dkfans/keeperfx | closed | Room roles for custom rooms are ignored | Priority-Medium Type-Defect | User made a custom room:
```ini
[slab41]
Name = SLAB41
BlockFlagsHeight = 4
BlockHealthIndex = 4
BlockFlags =
NoBlockFlags =
FillStyle = 0
Category = 5
SlbID = 4
Wibble = 1
IsSafeLand = 1
IsDiggable = 0
WlbType = 0
[room17]
Name = DEKOROOM
NameTextID = 191
TooltipTextID = 191
Cost = 0
Health = 100
SlabAssign = SLAB41
Roles =
Properties = CANNOT_VANDALIZE HAS_NO_ENSIGN
Messages = 0 0
EnvironmentSndSample = 0
TotalCapacity = none
UsedCapacity = none none
SymbolSprites = 0 0
PointerSprites = 0
PanelTabIndex = 0
```
He wants to be able to assign roles the the `Roles =` field, but says he can't. Possible not even to the default rooms either. | 1.0 | Room roles for custom rooms are ignored - User made a custom room:
```ini
[slab41]
Name = SLAB41
BlockFlagsHeight = 4
BlockHealthIndex = 4
BlockFlags =
NoBlockFlags =
FillStyle = 0
Category = 5
SlbID = 4
Wibble = 1
IsSafeLand = 1
IsDiggable = 0
WlbType = 0
[room17]
Name = DEKOROOM
NameTextID = 191
TooltipTextID = 191
Cost = 0
Health = 100
SlabAssign = SLAB41
Roles =
Properties = CANNOT_VANDALIZE HAS_NO_ENSIGN
Messages = 0 0
EnvironmentSndSample = 0
TotalCapacity = none
UsedCapacity = none none
SymbolSprites = 0 0
PointerSprites = 0
PanelTabIndex = 0
```
He wants to be able to assign roles the the `Roles =` field, but says he can't. Possible not even to the default rooms either. | defect | room roles for custom rooms are ignored user made a custom room ini name blockflagsheight blockhealthindex blockflags noblockflags fillstyle category slbid wibble issafeland isdiggable wlbtype name dekoroom nametextid tooltiptextid cost health slabassign roles properties cannot vandalize has no ensign messages environmentsndsample totalcapacity none usedcapacity none none symbolsprites pointersprites paneltabindex he wants to be able to assign roles the the roles field but says he can t possible not even to the default rooms either | 1 |
523,235 | 15,175,932,039 | IssuesEvent | 2021-02-14 02:02:09 | Poobslag/turbofat | https://api.github.com/repos/Poobslag/turbofat | closed | For levels with a goal like 'Finish in X:00 time', we should show a timer. | priority-3 | The timer shouldn't replace things like 'lines remaining', so we'll need to make room. | 1.0 | For levels with a goal like 'Finish in X:00 time', we should show a timer. - The timer shouldn't replace things like 'lines remaining', so we'll need to make room. | non_defect | for levels with a goal like finish in x time we should show a timer the timer shouldn t replace things like lines remaining so we ll need to make room | 0 |
347,721 | 24,896,575,165 | IssuesEvent | 2022-10-28 16:22:00 | dtcenter/METdataio | https://api.github.com/repos/dtcenter/METdataio | closed | Move release notes into its own chapter | priority: medium type: task component: documentation requestor: METplus Team | ## Describe the Task ##
Move the [METdataio Release Notes](https://metdataio.readthedocs.io/en/develop/Users_Guide/overview.html#met-release-notes) section out of the Overview chapter and into its own chapter (under Overview - the Release Notes will become chapter 2). Rename in the following way:
1.5 METdataio Release Notes -> 2 METdataio Release Information
Modify the index.rst file to add the new chapter "release-notes" after "overview"
Create a new 2.1 section called METdataio Release Notes
Remove these sections:
1.5.1. Version 2.0.0 release notes (2022-09-14)
1.5.1.1. Version 2.0.0 release notes (20220914)
Keep the beta3 release section. (It will have new chapter section numbers.)
And rename the beta sections to this:
METdataio Version 2.0.0-beta3 release notes (20220914)
METdataio Version 2.0.0-beta2 release notes (20220804)
METdataio Version 2.0.0-beta1 release notes (20220622)
Create a new 2.2 section called METdataio Upgrade Instructions (with paragraph text "Upgrade instructions will be listed here if they are applicable for this release.")
This work will require changing the types of headers to follow the standard guidelines:
https://www.sphinx-doc.org/en/master/usage/restructuredtext/basics.html
```
# with overline, for parts
* with overline, for chapters
=, for sections
-, for subsections
^, for subsubsections
“, for paragraphs
```
### Time Estimate ###
*Estimate the amount of work required here.*
* 1 day of work or less.*
### Sub-Issues ###
Consider breaking the task down into sub-issues.
- [ ] *Add a checkbox for each sub-issue here.*
### Relevant Deadlines ###
*MET-11.0.0-beta4 release?.*
### Funding Source ###
*2792541.*
## Define the Metadata ##
### Assignee ###
- [x] Select **engineer(s)** or **no engineer** required
- [ ] Select **scientist(s)** or **no scientist** required
### Labels ###
- [x] Select **component(s)**
- [x] Select **priority**
- [x] Select **requestor(s)**
### Projects and Milestone ###
- [x] Select **Repository** and/or **Organization** level **Project(s)** or add **alert: NEED PROJECT ASSIGNMENT** label
- [x] Select **Milestone** as the next official version or **Future Versions**
## Define Related Issue(s) ##
Consider the impact to the other METplus components.
- [x] [METplus](https://github.com/dtcenter/METplus/issues/new/choose), [MET](https://github.com/dtcenter/MET/issues/new/choose), [METdataio](https://github.com/dtcenter/METdataio/issues/new/choose), [METviewer](https://github.com/dtcenter/METviewer/issues/new/choose), [METexpress](https://github.com/dtcenter/METexpress/issues/new/choose), [METcalcpy](https://github.com/dtcenter/METcalcpy/issues/new/choose), [METplotpy](https://github.com/dtcenter/METplotpy/issues/new/choose)
## Task Checklist ##
See the [METplus Workflow](https://metplus.readthedocs.io/en/latest/Contributors_Guide/github_workflow.html) for details.
- [x] Complete the issue definition above, including the **Time Estimate** and **Funding Source**.
- [x] Fork this repository or create a branch of **develop**.
Branch name: `feature_<Issue Number>_<Description>`
- [x] Complete the development and test your changes.
- [ ] Add/update log messages for easier debugging.
- [ ] Add/update unit tests.
- [x] Add/update documentation.
- [x] Push local changes to GitHub.
- [x] Submit a pull request to merge into **develop**.
Pull request: `feature <Issue Number> <Description>`
- [x] Define the pull request metadata, as permissions allow.
Select: **Reviewer(s)** and **Development** issues
Select: **Repository** level development cycle **Project** for the next official release
Select: **Milestone** as the next official version
- [x] Iterate until the reviewer(s) accept and merge your changes.
- [x] Delete your fork or branch.
- [x] Close this issue.
| 1.0 | Move release notes into its own chapter - ## Describe the Task ##
Move the [METdataio Release Notes](https://metdataio.readthedocs.io/en/develop/Users_Guide/overview.html#met-release-notes) section out of the Overview chapter and into its own chapter (under Overview - the Release Notes will become chapter 2). Rename in the following way:
1.5 METdataio Release Notes -> 2 METdataio Release Information
Modify the index.rst file to add the new chapter "release-notes" after "overview"
Create a new 2.1 section called METdataio Release Notes
Remove these sections:
1.5.1. Version 2.0.0 release notes (2022-09-14)
1.5.1.1. Version 2.0.0 release notes (20220914)
Keep the beta3 release section. (It will have new chapter section numbers.)
And rename the beta sections to this:
METdataio Version 2.0.0-beta3 release notes (20220914)
METdataio Version 2.0.0-beta2 release notes (20220804)
METdataio Version 2.0.0-beta1 release notes (20220622)
Create a new 2.2 section called METdataio Upgrade Instructions (with paragraph text "Upgrade instructions will be listed here if they are applicable for this release.")
This work will require changing the types of headers to follow the standard guidelines:
https://www.sphinx-doc.org/en/master/usage/restructuredtext/basics.html
```
# with overline, for parts
* with overline, for chapters
=, for sections
-, for subsections
^, for subsubsections
“, for paragraphs
```
### Time Estimate ###
*Estimate the amount of work required here.*
* 1 day of work or less.*
### Sub-Issues ###
Consider breaking the task down into sub-issues.
- [ ] *Add a checkbox for each sub-issue here.*
### Relevant Deadlines ###
*MET-11.0.0-beta4 release?.*
### Funding Source ###
*2792541.*
## Define the Metadata ##
### Assignee ###
- [x] Select **engineer(s)** or **no engineer** required
- [ ] Select **scientist(s)** or **no scientist** required
### Labels ###
- [x] Select **component(s)**
- [x] Select **priority**
- [x] Select **requestor(s)**
### Projects and Milestone ###
- [x] Select **Repository** and/or **Organization** level **Project(s)** or add **alert: NEED PROJECT ASSIGNMENT** label
- [x] Select **Milestone** as the next official version or **Future Versions**
## Define Related Issue(s) ##
Consider the impact to the other METplus components.
- [x] [METplus](https://github.com/dtcenter/METplus/issues/new/choose), [MET](https://github.com/dtcenter/MET/issues/new/choose), [METdataio](https://github.com/dtcenter/METdataio/issues/new/choose), [METviewer](https://github.com/dtcenter/METviewer/issues/new/choose), [METexpress](https://github.com/dtcenter/METexpress/issues/new/choose), [METcalcpy](https://github.com/dtcenter/METcalcpy/issues/new/choose), [METplotpy](https://github.com/dtcenter/METplotpy/issues/new/choose)
## Task Checklist ##
See the [METplus Workflow](https://metplus.readthedocs.io/en/latest/Contributors_Guide/github_workflow.html) for details.
- [x] Complete the issue definition above, including the **Time Estimate** and **Funding Source**.
- [x] Fork this repository or create a branch of **develop**.
Branch name: `feature_<Issue Number>_<Description>`
- [x] Complete the development and test your changes.
- [ ] Add/update log messages for easier debugging.
- [ ] Add/update unit tests.
- [x] Add/update documentation.
- [x] Push local changes to GitHub.
- [x] Submit a pull request to merge into **develop**.
Pull request: `feature <Issue Number> <Description>`
- [x] Define the pull request metadata, as permissions allow.
Select: **Reviewer(s)** and **Development** issues
Select: **Repository** level development cycle **Project** for the next official release
Select: **Milestone** as the next official version
- [x] Iterate until the reviewer(s) accept and merge your changes.
- [x] Delete your fork or branch.
- [x] Close this issue.
| non_defect | move release notes into its own chapter describe the task move the section out of the overview chapter and into its own chapter under overview the release notes will become chapter rename in the following way metdataio release notes metdataio release information modify the index rst file to add the new chapter release notes after overview create a new section called metdataio release notes remove these sections version release notes version release notes keep the release section it will have new chapter section numbers and rename the beta sections to this metdataio version release notes metdataio version release notes metdataio version release notes create a new section called metdataio upgrade instructions with paragraph text upgrade instructions will be listed here if they are applicable for this release this work will require changing the types of headers to follow the standard guidelines with overline for parts with overline for chapters for sections for subsections for subsubsections “ for paragraphs time estimate estimate the amount of work required here day of work or less sub issues consider breaking the task down into sub issues add a checkbox for each sub issue here relevant deadlines met release funding source define the metadata assignee select engineer s or no engineer required select scientist s or no scientist required labels select component s select priority select requestor s projects and milestone select repository and or organization level project s or add alert need project assignment label select milestone as the next official version or future versions define related issue s consider the impact to the other metplus components task checklist see the for details complete the issue definition above including the time estimate and funding source fork this repository or create a branch of develop branch name feature complete the development and test your changes add update log messages for easier debugging add update unit tests add update documentation push local changes to github submit a pull request to merge into develop pull request feature define the pull request metadata as permissions allow select reviewer s and development issues select repository level development cycle project for the next official release select milestone as the next official version iterate until the reviewer s accept and merge your changes delete your fork or branch close this issue | 0 |
79,990 | 29,811,453,103 | IssuesEvent | 2023-06-16 15:21:51 | vector-im/element-desktop | https://api.github.com/repos/vector-im/element-desktop | opened | Chat does not properly render emjois | T-Defect | ### Steps to reproduce
1. Paste in or send (from another platform, e.g. iOS) a complicated emojii like 😶🌫️.
### Outcome
#### What did you expect?
I expect to see the 😶🌫️ emoji in the conversation.
#### What happened instead?
- In the chat window, the emoji will be displayed as 😶🌫️ (on desktop, on iOS it shows up properly).
- Interestingly, on the side panel which shows all conversation, the emojii is properly rendered as 😶🌫️.
### Operating system
MacOS and Ubuntu 23.04
### Application version
Element version: 1.11.33 Olm version: 3.2.14
### How did you install the app?
downloaded dmg for mac, apt-get install for linux
### Homeserver
_No response_
### Will you send logs?
No | 1.0 | Chat does not properly render emjois - ### Steps to reproduce
1. Paste in or send (from another platform, e.g. iOS) a complicated emojii like 😶🌫️.
### Outcome
#### What did you expect?
I expect to see the 😶🌫️ emoji in the conversation.
#### What happened instead?
- In the chat window, the emoji will be displayed as 😶🌫️ (on desktop, on iOS it shows up properly).
- Interestingly, on the side panel which shows all conversation, the emojii is properly rendered as 😶🌫️.
### Operating system
MacOS and Ubuntu 23.04
### Application version
Element version: 1.11.33 Olm version: 3.2.14
### How did you install the app?
downloaded dmg for mac, apt-get install for linux
### Homeserver
_No response_
### Will you send logs?
No | defect | chat does not properly render emjois steps to reproduce paste in or send from another platform e g ios a complicated emojii like 😶🌫️ outcome what did you expect i expect to see the 😶🌫️ emoji in the conversation what happened instead in the chat window the emoji will be displayed as 😶🌫️ on desktop on ios it shows up properly interestingly on the side panel which shows all conversation the emojii is properly rendered as 😶🌫️ operating system macos and ubuntu application version element version olm version how did you install the app downloaded dmg for mac apt get install for linux homeserver no response will you send logs no | 1 |
45,713 | 13,042,048,730 | IssuesEvent | 2020-07-28 21:35:39 | stressapptest/stressapptest | https://api.github.com/repos/stressapptest/stressapptest | closed | stressapptest can not complete and system does not hang up | Priority-Medium Type-Defect auto-migrated | ```
What steps will reproduce the problem?
1.Commandline - stressapptest -f /mnt/1 --filesize 1024000 -s 216000 -l
stress_60hr_sys5_8T
What is the expected output? What do you see instead?
1. stressapptest can not complete and system does not hang up
2. The screen show "Pausing worker threads in preparation for power spike(35400
seconds remaining)"
What version of the product are you using? On what operating system?
1. Stressapptest : SAT revision 1.0.5_autoconf, 64 bit binary
2. OS : CentOS6.4
Please provide any additional information below.
```
Original issue reported on code.google.com by `plok...@gmail.com` on 13 Oct 2014 at 10:13
Attachments:
- [stress_60hr_sys5_8T](https://storage.googleapis.com/google-code-attachments/stressapptest/issue-37/comment-0/stress_60hr_sys5_8T)
| 1.0 | stressapptest can not complete and system does not hang up - ```
What steps will reproduce the problem?
1.Commandline - stressapptest -f /mnt/1 --filesize 1024000 -s 216000 -l
stress_60hr_sys5_8T
What is the expected output? What do you see instead?
1. stressapptest can not complete and system does not hang up
2. The screen show "Pausing worker threads in preparation for power spike(35400
seconds remaining)"
What version of the product are you using? On what operating system?
1. Stressapptest : SAT revision 1.0.5_autoconf, 64 bit binary
2. OS : CentOS6.4
Please provide any additional information below.
```
Original issue reported on code.google.com by `plok...@gmail.com` on 13 Oct 2014 at 10:13
Attachments:
- [stress_60hr_sys5_8T](https://storage.googleapis.com/google-code-attachments/stressapptest/issue-37/comment-0/stress_60hr_sys5_8T)
| defect | stressapptest can not complete and system does not hang up what steps will reproduce the problem commandline stressapptest f mnt filesize s l stress what is the expected output what do you see instead stressapptest can not complete and system does not hang up the screen show pausing worker threads in preparation for power spike seconds remaining what version of the product are you using on what operating system stressapptest sat revision autoconf bit binary os please provide any additional information below original issue reported on code google com by plok gmail com on oct at attachments | 1 |
15,375 | 19,600,400,347 | IssuesEvent | 2022-01-06 00:11:06 | pods-framework/pods | https://api.github.com/repos/pods-framework/pods | closed | Block attributes are not always strings | Type: Bug Focus: Other Compatibility | The block render functions in this plugin assume that all block attributes are strings:
[`$attributes = array_map( 'trim', $attributes );`](https://github.com/pods-framework/pods/blob/2b6e56a7e175bcb61e0b21664fc1064edf0ab5c2/src/Pods/Blocks/Types/Item_List.php#L372)
causing a warning:
`Warning: trim() expects parameter 1 to be string`
Block attributes can be extended by [third party plugins](https://wordpress.org/support/topic/problem-with-another-plugin-4/) so that should ideally be accounted for. | True | Block attributes are not always strings - The block render functions in this plugin assume that all block attributes are strings:
[`$attributes = array_map( 'trim', $attributes );`](https://github.com/pods-framework/pods/blob/2b6e56a7e175bcb61e0b21664fc1064edf0ab5c2/src/Pods/Blocks/Types/Item_List.php#L372)
causing a warning:
`Warning: trim() expects parameter 1 to be string`
Block attributes can be extended by [third party plugins](https://wordpress.org/support/topic/problem-with-another-plugin-4/) so that should ideally be accounted for. | non_defect | block attributes are not always strings the block render functions in this plugin assume that all block attributes are strings causing a warning warning trim expects parameter to be string block attributes can be extended by so that should ideally be accounted for | 0 |
746,538 | 26,034,131,775 | IssuesEvent | 2022-12-22 01:54:16 | OSU-Sustainability-Office/energy-dashboard | https://api.github.com/repos/OSU-Sustainability-Office/energy-dashboard | closed | Frontend Breaks on Node versions > 12 | bug priority-low | If not running node version 12, the frontend will fail to build (e.g., using node 14 or above).
I think we can fix this by adjusting our package.json to specifically use the older versions of dependencies used in the dashboard but might take a bit to iron out. | 1.0 | Frontend Breaks on Node versions > 12 - If not running node version 12, the frontend will fail to build (e.g., using node 14 or above).
I think we can fix this by adjusting our package.json to specifically use the older versions of dependencies used in the dashboard but might take a bit to iron out. | non_defect | frontend breaks on node versions if not running node version the frontend will fail to build e g using node or above i think we can fix this by adjusting our package json to specifically use the older versions of dependencies used in the dashboard but might take a bit to iron out | 0 |
45,230 | 12,678,832,678 | IssuesEvent | 2020-06-19 10:30:49 | primefaces/primeng | https://api.github.com/repos/primefaces/primeng | closed | p-inputNumber ignores disabled state in reactive forms | defect | **I'm submitting a ...** (check one with "x")
```
[X ] bug report => Search github for a similar issue or PR before submitting
[ ] feature request => Please check if request is not on the roadmap already https://github.com/primefaces/primeng/wiki/Roadmap
[ ] support request => Please do not submit support request here, instead see http://forum.primefaces.org/viewforum.php?f=35
```
**Plunkr Case (Bug Reports)**
Please demonstrate your case at stackblitz by using the issue template below. Issues without a test case have much less possibility to be reviewd in detail and assisted.
https://stackblitz.com/edit/github-1svgpy
**Current behavior**
Form field does not disable
**Expected behavior**
Form field is disabled when it is set to be disabled.
**Minimal reproduction of the problem with instructions**
See Stackblitz above for functional example.
If the reactive form uses p-inputNumber and it's set to disabled, the control does not disable.
HTML
```<p-inputNumber id="limit" formControlName="limit" mode="decimal" [minFractionDigits]="selectedTradedInstrument?.sgfntPriceDecimals"></p-inputNumber>```
Form creation
```limit: [{value: 0, disabled: true}, [Validators.required]],```
* **Angular version:** 5.X
8.2.3
* **PrimeNG version:** 5.X
9.1.0
* **Browser:** [all | Chrome XX | Firefox XX | IE XX | Safari XX | Mobile Chrome XX | Android X.X Web Browser | iOS XX Safari | iOS XX UIWebView | iOS XX WKWebView ]
Chrome Latest
* **Language:** [all | TypeScript X.X | ES6/7 | ES5]
Typescript 3.5.3
| 1.0 | p-inputNumber ignores disabled state in reactive forms - **I'm submitting a ...** (check one with "x")
```
[X ] bug report => Search github for a similar issue or PR before submitting
[ ] feature request => Please check if request is not on the roadmap already https://github.com/primefaces/primeng/wiki/Roadmap
[ ] support request => Please do not submit support request here, instead see http://forum.primefaces.org/viewforum.php?f=35
```
**Plunkr Case (Bug Reports)**
Please demonstrate your case at stackblitz by using the issue template below. Issues without a test case have much less possibility to be reviewd in detail and assisted.
https://stackblitz.com/edit/github-1svgpy
**Current behavior**
Form field does not disable
**Expected behavior**
Form field is disabled when it is set to be disabled.
**Minimal reproduction of the problem with instructions**
See Stackblitz above for functional example.
If the reactive form uses p-inputNumber and it's set to disabled, the control does not disable.
HTML
```<p-inputNumber id="limit" formControlName="limit" mode="decimal" [minFractionDigits]="selectedTradedInstrument?.sgfntPriceDecimals"></p-inputNumber>```
Form creation
```limit: [{value: 0, disabled: true}, [Validators.required]],```
* **Angular version:** 5.X
8.2.3
* **PrimeNG version:** 5.X
9.1.0
* **Browser:** [all | Chrome XX | Firefox XX | IE XX | Safari XX | Mobile Chrome XX | Android X.X Web Browser | iOS XX Safari | iOS XX UIWebView | iOS XX WKWebView ]
Chrome Latest
* **Language:** [all | TypeScript X.X | ES6/7 | ES5]
Typescript 3.5.3
| defect | p inputnumber ignores disabled state in reactive forms i m submitting a check one with x bug report search github for a similar issue or pr before submitting feature request please check if request is not on the roadmap already support request please do not submit support request here instead see plunkr case bug reports please demonstrate your case at stackblitz by using the issue template below issues without a test case have much less possibility to be reviewd in detail and assisted current behavior form field does not disable expected behavior form field is disabled when it is set to be disabled minimal reproduction of the problem with instructions see stackblitz above for functional example if the reactive form uses p inputnumber and it s set to disabled the control does not disable html form creation limit angular version x primeng version x browser chrome latest language typescript | 1 |
28,350 | 5,241,424,440 | IssuesEvent | 2017-01-31 15:41:10 | google/google-toolbox-for-mac | https://api.github.com/repos/google/google-toolbox-for-mac | closed | Leak detection not working on Lion | auto-migrated Priority-Medium Type-Defect | ```
What steps will reproduce the problem?
1. set GTM_ENABLE_LEAKS=1
2. Run a test triggering a leak
What is the expected output?
On Snow Leopard the following messages are printed and the leak is detected
leaks Report Version: 2.0
Process 73650: 16 leaks for 464 total leaked bytes.
What do you see instead?
On Lion, only the following message is printed and no leaks are detected.
leaks Report Version: 2.0
What version of the product are you using? On what operating system?
Lion: Xcode 4.3.1 Build version 4E1019
Please provide any additional information below.
```
Original issue reported on code.google.com by `rob...@google.com` on 26 Apr 2012 at 7:50
| 1.0 | Leak detection not working on Lion - ```
What steps will reproduce the problem?
1. set GTM_ENABLE_LEAKS=1
2. Run a test triggering a leak
What is the expected output?
On Snow Leopard the following messages are printed and the leak is detected
leaks Report Version: 2.0
Process 73650: 16 leaks for 464 total leaked bytes.
What do you see instead?
On Lion, only the following message is printed and no leaks are detected.
leaks Report Version: 2.0
What version of the product are you using? On what operating system?
Lion: Xcode 4.3.1 Build version 4E1019
Please provide any additional information below.
```
Original issue reported on code.google.com by `rob...@google.com` on 26 Apr 2012 at 7:50
| defect | leak detection not working on lion what steps will reproduce the problem set gtm enable leaks run a test triggering a leak what is the expected output on snow leopard the following messages are printed and the leak is detected leaks report version process leaks for total leaked bytes what do you see instead on lion only the following message is printed and no leaks are detected leaks report version what version of the product are you using on what operating system lion xcode build version please provide any additional information below original issue reported on code google com by rob google com on apr at | 1 |
16,131 | 11,848,226,313 | IssuesEvent | 2020-03-24 13:27:12 | patternfly/patternfly-react | https://api.github.com/repos/patternfly/patternfly-react | opened | Remove storybook from pf-react-seed repo | infrastructure | The seed application should be streamlined for startup applications and not component development.
- Remove storybook
| 1.0 | Remove storybook from pf-react-seed repo - The seed application should be streamlined for startup applications and not component development.
- Remove storybook
| non_defect | remove storybook from pf react seed repo the seed application should be streamlined for startup applications and not component development remove storybook | 0 |
13,384 | 2,755,121,429 | IssuesEvent | 2015-04-26 10:35:46 | bridgedotnet/Bridge | https://api.github.com/repos/bridgedotnet/Bridge | closed | Linq Intersect() does not work | defect | C# code:
```C#
using System;
using System.Collections.Generic;
using System.Linq;
using Bridge;
namespace Demo
{
public class App
{
[Ready]
public static void Main()
{
int[] a = { 1, 2 };
int[] b = { 1, 2 };
var result = a.Intersect(b).ToArray();
}
}
}
```
Translates to
```javascript
var a = [1, 2];
var b = [1, 2];
var result = Bridge.Linq.Enumerable.from().intersect().toArray();
```
Please note it was working last Friday. | 1.0 | Linq Intersect() does not work - C# code:
```C#
using System;
using System.Collections.Generic;
using System.Linq;
using Bridge;
namespace Demo
{
public class App
{
[Ready]
public static void Main()
{
int[] a = { 1, 2 };
int[] b = { 1, 2 };
var result = a.Intersect(b).ToArray();
}
}
}
```
Translates to
```javascript
var a = [1, 2];
var b = [1, 2];
var result = Bridge.Linq.Enumerable.from().intersect().toArray();
```
Please note it was working last Friday. | defect | linq intersect does not work c code c using system using system collections generic using system linq using bridge namespace demo public class app public static void main int a int b var result a intersect b toarray translates to javascript var a var b var result bridge linq enumerable from intersect toarray please note it was working last friday | 1 |
9,241 | 2,615,140,907 | IssuesEvent | 2015-03-01 06:15:27 | chrsmith/reaver-wps | https://api.github.com/repos/chrsmith/reaver-wps | closed | WARNING: Failed to associate with.. | auto-migrated Priority-Medium Type-Defect | ```
What steps will reproduce the problem?
I use reaver 1.3 and backtrack 4 r2
2 wificards:
1) ath5k
2) rt2800usb
What is the expected output? What do you see instead?
---> Using Ath5k i can see this:
reaver -i mon0 -b 00:21:63:XX:XX:XX -vv
Reaver v1.3 WiFi Protected Setup Attack Tool
Copyright (c) 2011, Tactical Network Solutions, Craig Heffner
<cheffner@tacnetsol.com>
[+] Waiting for beacon from 00:21:63:XX:XX:XX
[+] Switching mon0 to channel 2
[+] Switching mon0 to channel 3
[+] Switching mon0 to channel 4
[+] Switching mon0 to channel 5
[+] Switching mon0 to channel 6
[+] Switching mon0 to channel 7
[+] Switching mon0 to channel 8
[+] Switching mon0 to channel 9
[+] Switching mon0 to channel 10
[+] Switching mon0 to channel 11
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[+] Associated with 00:21:63:XX:XX:XX (ESSID: VodafoneXXX)
[+] Trying pin 70211382
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[+] Switching mon0 to channel 11
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
---> Using rt2800usb this:
root@bt:~/WPS/reaver-1.3/src# reaver -i mon0 -b 00:21:63:EF:F7:26 -vv
Reaver v1.3 WiFi Protected Setup Attack Tool
Copyright (c) 2011, Tactical Network Solutions, Craig Heffner <cheffner@tacnetso
l.com>
[+] Waiting for beacon from 00:21:63:EF:F7:26
[+] Switching mon0 to channel 2
[+] Switching mon0 to channel 3
[+] Switching mon0 to channel 4
[+] Switching mon0 to channel 5
[+] Switching mon0 to channel 6
[+] Switching mon0 to channel 7
[+] Switching mon0 to channel 8
[+] Switching mon0 to channel 9
[+] Switching mon0 to channel 10
[+] Switching mon0 to channel 11
[+] Switching mon0 to channel 11
[+] Associated with 00:21:63:EF:F7:26 (ESSID: VodafoneF725)
[+] Trying pin 15055972
[!] WARNING: Failed to associate with 00:21:63:EF:F7:26 (ESSID: VodafoneF725)
[+] Switching mon0 to channel 12
[!] WARNING: Failed to associate with 00:21:63:EF:F7:26 (ESSID: VodafoneF725)
[+] Switching mon0 to channel 13
[!] WARNING: Receive timeout occurred
[!] WARNING: Receive timeout occurred
[!] WARNING: Receive timeout occurred
[!] WARNING: Receive timeout occurred
[!] WARNING: Receive timeout occurred
.
.
.
[!] WARNING: 25 successive start failures
What version of the product are you using? On what operating system?
Reaver 1.3 download from here.
Please provide any additional information below.
I upload the pcap of the 2 wificards.
Any idea of the error, the AP is not vulnerate?
Thanks a lot for your work..
```
Original issue reported on code.google.com by `mikereav...@gmail.com` on 4 Jan 2012 at 7:39
Attachments:
* [Vodafone-rt2800sb.zip](https://storage.googleapis.com/google-code-attachments/reaver-wps/issue-75/comment-0/Vodafone-rt2800sb.zip)
* [Vodafone-Ath5K.zip](https://storage.googleapis.com/google-code-attachments/reaver-wps/issue-75/comment-0/Vodafone-Ath5K.zip)
| 1.0 | WARNING: Failed to associate with.. - ```
What steps will reproduce the problem?
I use reaver 1.3 and backtrack 4 r2
2 wificards:
1) ath5k
2) rt2800usb
What is the expected output? What do you see instead?
---> Using Ath5k i can see this:
reaver -i mon0 -b 00:21:63:XX:XX:XX -vv
Reaver v1.3 WiFi Protected Setup Attack Tool
Copyright (c) 2011, Tactical Network Solutions, Craig Heffner
<cheffner@tacnetsol.com>
[+] Waiting for beacon from 00:21:63:XX:XX:XX
[+] Switching mon0 to channel 2
[+] Switching mon0 to channel 3
[+] Switching mon0 to channel 4
[+] Switching mon0 to channel 5
[+] Switching mon0 to channel 6
[+] Switching mon0 to channel 7
[+] Switching mon0 to channel 8
[+] Switching mon0 to channel 9
[+] Switching mon0 to channel 10
[+] Switching mon0 to channel 11
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[+] Associated with 00:21:63:XX:XX:XX (ESSID: VodafoneXXX)
[+] Trying pin 70211382
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
[+] Switching mon0 to channel 11
[!] WARNING: Failed to associate with 00:21:63:XX:XX:XX (ESSID: VodafoneXXXX)
---> Using rt2800usb this:
root@bt:~/WPS/reaver-1.3/src# reaver -i mon0 -b 00:21:63:EF:F7:26 -vv
Reaver v1.3 WiFi Protected Setup Attack Tool
Copyright (c) 2011, Tactical Network Solutions, Craig Heffner <cheffner@tacnetso
l.com>
[+] Waiting for beacon from 00:21:63:EF:F7:26
[+] Switching mon0 to channel 2
[+] Switching mon0 to channel 3
[+] Switching mon0 to channel 4
[+] Switching mon0 to channel 5
[+] Switching mon0 to channel 6
[+] Switching mon0 to channel 7
[+] Switching mon0 to channel 8
[+] Switching mon0 to channel 9
[+] Switching mon0 to channel 10
[+] Switching mon0 to channel 11
[+] Switching mon0 to channel 11
[+] Associated with 00:21:63:EF:F7:26 (ESSID: VodafoneF725)
[+] Trying pin 15055972
[!] WARNING: Failed to associate with 00:21:63:EF:F7:26 (ESSID: VodafoneF725)
[+] Switching mon0 to channel 12
[!] WARNING: Failed to associate with 00:21:63:EF:F7:26 (ESSID: VodafoneF725)
[+] Switching mon0 to channel 13
[!] WARNING: Receive timeout occurred
[!] WARNING: Receive timeout occurred
[!] WARNING: Receive timeout occurred
[!] WARNING: Receive timeout occurred
[!] WARNING: Receive timeout occurred
.
.
.
[!] WARNING: 25 successive start failures
What version of the product are you using? On what operating system?
Reaver 1.3 download from here.
Please provide any additional information below.
I upload the pcap of the 2 wificards.
Any idea of the error, the AP is not vulnerate?
Thanks a lot for your work..
```
Original issue reported on code.google.com by `mikereav...@gmail.com` on 4 Jan 2012 at 7:39
Attachments:
* [Vodafone-rt2800sb.zip](https://storage.googleapis.com/google-code-attachments/reaver-wps/issue-75/comment-0/Vodafone-rt2800sb.zip)
* [Vodafone-Ath5K.zip](https://storage.googleapis.com/google-code-attachments/reaver-wps/issue-75/comment-0/Vodafone-Ath5K.zip)
| defect | warning failed to associate with what steps will reproduce the problem i use reaver and backtrack wificards what is the expected output what do you see instead using i can see this reaver i b xx xx xx vv reaver wifi protected setup attack tool copyright c tactical network solutions craig heffner waiting for beacon from xx xx xx switching to channel switching to channel switching to channel switching to channel switching to channel switching to channel switching to channel switching to channel switching to channel switching to channel warning failed to associate with xx xx xx essid vodafonexxxx warning failed to associate with xx xx xx essid vodafonexxxx warning failed to associate with xx xx xx essid vodafonexxxx warning failed to associate with xx xx xx essid vodafonexxxx warning failed to associate with xx xx xx essid vodafonexxxx warning failed to associate with xx xx xx essid vodafonexxxx warning failed to associate with xx xx xx essid vodafonexxxx warning failed to associate with xx xx xx essid vodafonexxxx warning failed to associate with xx xx xx essid vodafonexxxx warning failed to associate with xx xx xx essid vodafonexxxx associated with xx xx xx essid vodafonexxx trying pin warning failed to associate with xx xx xx essid vodafonexxxx switching to channel warning failed to associate with xx xx xx essid vodafonexxxx using this root bt wps reaver src reaver i b ef vv reaver wifi protected setup attack tool copyright c tactical network solutions craig heffner cheffner tacnetso l com waiting for beacon from ef switching to channel switching to channel switching to channel switching to channel switching to channel switching to channel switching to channel switching to channel switching to channel switching to channel switching to channel associated with ef essid trying pin warning failed to associate with ef essid switching to channel warning failed to associate with ef essid switching to channel warning receive timeout occurred warning receive timeout occurred warning receive timeout occurred warning receive timeout occurred warning receive timeout occurred warning successive start failures what version of the product are you using on what operating system reaver download from here please provide any additional information below i upload the pcap of the wificards any idea of the error the ap is not vulnerate thanks a lot for your work original issue reported on code google com by mikereav gmail com on jan at attachments | 1 |
2,569 | 2,978,300,562 | IssuesEvent | 2015-07-16 04:45:05 | facebook/osquery | https://api.github.com/repos/facebook/osquery | closed | Homebrew install of 1.4.7 doesn't include osqueryctl | build/test infrastructure user experience | It appears in the current (1.4.7) install of osquery from Homebrew.
<img width="741" alt="screen_shot_2015-07-15_at_8_54_37_am" src="https://cloud.githubusercontent.com/assets/44774/8704658/305334da-2ad9-11e5-8cf7-48a13e78490f.png">
This was installed today (July 15) with ```brew install osquery```. | 1.0 | Homebrew install of 1.4.7 doesn't include osqueryctl - It appears in the current (1.4.7) install of osquery from Homebrew.
<img width="741" alt="screen_shot_2015-07-15_at_8_54_37_am" src="https://cloud.githubusercontent.com/assets/44774/8704658/305334da-2ad9-11e5-8cf7-48a13e78490f.png">
This was installed today (July 15) with ```brew install osquery```. | non_defect | homebrew install of doesn t include osqueryctl it appears in the current install of osquery from homebrew img width alt screen shot at am src this was installed today july with brew install osquery | 0 |
29,006 | 5,476,192,452 | IssuesEvent | 2017-03-11 18:25:25 | richgel999/miniz | https://api.github.com/repos/richgel999/miniz | closed | Package Pre-Built Binaries Separately | auto-migrated Priority-Medium Type-Defect | ```
I would like to suggest that the pre-built binaries be packaged separately from
the source code. The intent would be to better facilitate Linux distribution
packaging. Fedora, for example, does not permit pre-built binaries in its
packages.
See:
http://fedoraproject.org/wiki/Packaging:Guidelines#No_inclusion_of_pre-built_bin
aries_or_libraries
Thank you for for considering.
```
Original issue reported on code.google.com by `stalb...@gmail.com` on 15 Oct 2014 at 2:54
| 1.0 | Package Pre-Built Binaries Separately - ```
I would like to suggest that the pre-built binaries be packaged separately from
the source code. The intent would be to better facilitate Linux distribution
packaging. Fedora, for example, does not permit pre-built binaries in its
packages.
See:
http://fedoraproject.org/wiki/Packaging:Guidelines#No_inclusion_of_pre-built_bin
aries_or_libraries
Thank you for for considering.
```
Original issue reported on code.google.com by `stalb...@gmail.com` on 15 Oct 2014 at 2:54
| defect | package pre built binaries separately i would like to suggest that the pre built binaries be packaged separately from the source code the intent would be to better facilitate linux distribution packaging fedora for example does not permit pre built binaries in its packages see aries or libraries thank you for for considering original issue reported on code google com by stalb gmail com on oct at | 1 |
298,244 | 9,197,541,386 | IssuesEvent | 2019-03-07 10:14:29 | yalla-coop/tempo | https://api.github.com/repos/yalla-coop/tempo | opened | Harmonize styled components | T2h priority-4 | A lot of the pages use their own wrappers and use form, input, label components which could be harmonized. This will make the look of the entire platform a lot more consistent. | 1.0 | Harmonize styled components - A lot of the pages use their own wrappers and use form, input, label components which could be harmonized. This will make the look of the entire platform a lot more consistent. | non_defect | harmonize styled components a lot of the pages use their own wrappers and use form input label components which could be harmonized this will make the look of the entire platform a lot more consistent | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.