Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 757 | labels stringlengths 4 664 | body stringlengths 3 261k | index stringclasses 10 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 232k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
11,399 | 2,650,682,472 | IssuesEvent | 2015-03-16 02:57:58 | hkwi/python-geohash | https://api.github.com/repos/hkwi/python-geohash | closed | Compatible with Py3k, fixed cpp code warning and styles | auto-migrated Priority-Medium Type-Defect | ```
I was trying to use python-geohash on Python 3.4.0. But it didn't work.
So I updated the code for py2k and py3k compatible.
All the codes are hosted on Github: https://github.com/zonyitoo/python-geohash
I hope it can be merged into the main stream. Thanks.
```
Original issue reported on code.google.com by `zonyi...@gmail.com` on 17 May 2014 at 5:40 | 1.0 | Compatible with Py3k, fixed cpp code warning and styles - ```
I was trying to use python-geohash on Python 3.4.0. But it didn't work.
So I updated the code for py2k and py3k compatible.
All the codes are hosted on Github: https://github.com/zonyitoo/python-geohash
I hope it can be merged into the main stream. Thanks.
```
Original issue reported on code.google.com by `zonyi...@gmail.com` on 17 May 2014 at 5:40 | defect | compatible with fixed cpp code warning and styles i was trying to use python geohash on python but it didn t work so i updated the code for and compatible all the codes are hosted on github i hope it can be merged into the main stream thanks original issue reported on code google com by zonyi gmail com on may at | 1 |
22,408 | 11,730,670,841 | IssuesEvent | 2020-03-10 21:54:34 | Azure/azure-powershell | https://api.github.com/repos/Azure/azure-powershell | reopened | We will be required to enable singlePlacementGroup even though you have not enabled AutomaticRepairsPolicy when we deploying VMSS using New-AzVmss. | Compute - VMSS Service Attention customer-reported |
## Description
When we deploy new VMSS under APPGW whose health prove is enabled, the error message is occurred.
I don't choose " -EnableAutomaticRepair " option in "New-AzVmssConfig".
However, the error message tells me that you should enable "singlePlacementGroup" to deply VMSS.
When I tried in Ver Az 1.1.0, same error is not occurred.
I and Cx confirmed that same error is occurred in Az 3.5.0 and 3.1.0.
I think that this reason is "Automatic repairs feature" is newer function.
PS C:\Users\koyasuda> Get-InstalledModule -Name Az -AllVersions | select Name,Version
Name Version
---- -------
Az 1.1.0
Az 3.5.0
when I deployed single VMSS(not under APPGW), the same error is not occurred.
## Steps to reproduce
I attached my scripts.
==========================
$vnet = Get-AzVirtualNetwork `
-ResourceGroupName $rgname `
-Name $vnet.Name
$appgw = Get-AzApplicationGateway `
-ResourceGroupName $rgname `
-Name $appgwName
$backendPool = Get-AzApplicationGatewayBackendAddressPool `
-Name $defaultPool.Name `
-ApplicationGateway $appgw
$ipConfig = New-AzVmssIpConfig `
-Name $gipconfig.Name `
-SubnetId $vnet.Subnets[0].Id `
-ApplicationGatewayBackendAddressPoolsId $backendPool.Id
$vmssConfig = New-AzVmssConfig `
-Location japaneast `
-SkuCapacity 2 `
-SkuName Standard_DS2_v2 `
-UpgradePolicyMode Automatic `
-Zone @("1", "2", "3")
$vmImage = Get-AzImage -ResourceGroupName $rgname -ImageName $vmImageName
Set-AzVmssStorageProfile $vmssConfig -ImageReferenceId $vmImage.Id -OsDiskCreateOption "FromImage"
Set-AzVmssOsProfile $vmssConfig `
-AdminUsername $vmssAdminUserName `
-AdminPassword $vmssAdminPassword `
-ComputerNamePrefix $scaleSetName
Add-AzVmssNetworkInterfaceConfiguration `
-VirtualMachineScaleSet $vmssConfig `
-Name "NetConfig" `
-Primary $true `
-IPConfiguration $ipConfig
New-AzVmss -ResourceGroupName $rgname -Name $scaleSetName -VirtualMachineScaleSet $vmssConfig -Debug
==========================
## Environment data
PS C:\Users\koyasuda> $PSVersionTable
Name Value
---- -----
PSVersion 5.1.18362.628
PSEdition Desktop
PSCompatibleVersions {1.0, 2.0, 3.0, 4.0...}
BuildVersion 10.0.18362.628
CLRVersion 4.0.30319.42000
WSManStackVersion 3.0
PSRemotingProtocolVersion 2.3
SerializationVersion 1.1.0.1
## Module versions
<!-- Please run (Get-Module -ListAvailable) and paste the output in the below code block -->
ModuleType Version Name ExportedCommands
---------- ------- ---- ----------------
Manifest 1.0.0.0 AppBackgroundTask {Disable-AppBackgroundTaskDiagnosticLog, Enable-AppBackgroundTaskDiagnosticLog, Set-AppBackgroundTaskResourcePolicy, Unregister-Ap...
Manifest 2.0.0.0 AppLocker {Get-AppLockerFileInformation, Get-AppLockerPolicy, New-AppLockerPolicy, Set-AppLockerPolicy...}
Manifest 1.0.0.0 AppvClient {Add-AppvClientConnectionGroup, Add-AppvClientPackage, Add-AppvPublishingServer, Disable-Appv...}
Manifest 2.0.1.0 Appx {Add-AppxPackage, Get-AppxPackage, Get-AppxPackageManifest, Remove-AppxPackage...}
Script 1.0.0.0 AssignedAccess {Clear-AssignedAccess, Get-AssignedAccess, Set-AssignedAccess}
Manifest 1.0.0.0 BitLocker {Unlock-BitLocker, Suspend-BitLocker, Resume-BitLocker, Remove-BitLockerKeyProtector...}
Manifest 2.0.0.0 BitsTransfer {Add-BitsFile, Complete-BitsTransfer, Get-BitsTransfer, Remove-BitsTransfer...}
Manifest 1.0.0.0 BranchCache {Add-BCDataCacheExtension, Clear-BCCache, Disable-BC, Disable-BCDowngrading...}
Manifest 1.0.0.0 CimCmdlets {Get-CimAssociatedInstance, Get-CimClass, Get-CimInstance, Get-CimSession...}
Manifest 1.0 ConfigCI {Get-SystemDriver, New-CIPolicyRule, New-CIPolicy, Get-CIPolicy...}
Manifest 1.0 ConfigDefender {Get-MpPreference, Set-MpPreference, Add-MpPreference, Remove-MpPreference...}
Manifest 1.0 Defender {Get-MpPreference, Set-MpPreference, Add-MpPreference, Remove-MpPreference...}
Manifest 1.0.2.0 DeliveryOptimization {Delete-DeliveryOptimizationCache, Get-DeliveryOptimizationStatus, Set-DeliveryOptimizationStatus, Get-DeliveryOptimizationPerfSna...
Manifest 1.0.0.0 DirectAccessClientComponents {Disable-DAManualEntryPointSelection, Enable-DAManualEntryPointSelection, Get-DAClientExperienceConfiguration, Get-DAEntryPointTab...
Script 3.0 Dism {Add-AppxProvisionedPackage, Add-WindowsDriver, Add-WindowsCapability, Add-WindowsImage...}
Manifest 1.0.0.0 DnsClient {Resolve-DnsName, Clear-DnsClientCache, Get-DnsClient, Get-DnsClientCache...}
Manifest 1.0.0.0 EventTracingManagement {Start-EtwTraceSession, New-EtwTraceSession, Get-EtwTraceSession, Update-EtwTraceSession...}
Manifest 1.0.0.0 HgsClient {Get-HgsAttestationBaselinePolicy, Get-HgsClientConfiguration, Test-HgsClientConfiguration, Set-HgsClientConfiguration...}
Manifest 1.0.0.0 HgsDiagnostics {New-HgsTraceTarget, Get-HgsTrace, Get-HgsTraceFileData, Test-HgsTraceTarget}
Manifest 1.0.0.1 HostNetworkingService {Remove-HnsNamespace, Remove-HnsEndpoint, Get-HnsEndpoint, Get-HnsNamespace...}
Binary 2.0.0.0 Hyper-V {Add-VMAssignableDevice, Add-VMDvdDrive, Add-VMFibreChannelHba, Add-VMGpuPartitionAdapter...}
Binary 1.1 Hyper-V {Add-VMDvdDrive, Add-VMFibreChannelHba, Add-VMHardDiskDrive, Add-VMMigrationNetwork...}
Manifest 2.0.0.0 International {Get-WinDefaultInputMethodOverride, Set-WinDefaultInputMethodOverride, Get-WinHomeLocation, Set-WinHomeLocation...}
Manifest 1.0.0.0 iSCSI {Get-IscsiTargetPortal, New-IscsiTargetPortal, Remove-IscsiTargetPortal, Update-IscsiTargetPortal...}
Script 1.0.0.0 ISE {New-IseSnippet, Import-IseSnippet, Get-IseSnippet}
Manifest 1.0.0.0 Kds {Add-KdsRootKey, Get-KdsRootKey, Test-KdsRootKey, Set-KdsConfiguration...}
Manifest 1.0.1.0 Microsoft.PowerShell.Archive {Compress-Archive, Expand-Archive}
Manifest 3.0.0.0 Microsoft.PowerShell.Diagnostics {Get-WinEvent, Get-Counter, Import-Counter, Export-Counter...}
Manifest 3.0.0.0 Microsoft.PowerShell.Host {Start-Transcript, Stop-Transcript}
Manifest 1.0.0.0 Microsoft.PowerShell.LocalAccounts {Add-LocalGroupMember, Disable-LocalUser, Enable-LocalUser, Get-LocalGroup...}
Manifest 3.1.0.0 Microsoft.PowerShell.Management {Add-Content, Clear-Content, Clear-ItemProperty, Join-Path...}
Script 1.0 Microsoft.PowerShell.ODataUtils Export-ODataEndpointProxy
Manifest 3.0.0.0 Microsoft.PowerShell.Security {Get-Acl, Set-Acl, Get-PfxCertificate, Get-Credential...}
Manifest 3.1.0.0 Microsoft.PowerShell.Utility {Format-List, Format-Custom, Format-Table, Format-Wide...}
Manifest 3.0.0.0 Microsoft.WSMan.Management {Disable-WSManCredSSP, Enable-WSManCredSSP, Get-WSManCredSSP, Set-WSManQuickConfig...}
Manifest 1.0 MMAgent {Disable-MMAgent, Enable-MMAgent, Set-MMAgent, Get-MMAgent...}
Manifest 1.0.0.0 MsDtc {New-DtcDiagnosticTransaction, Complete-DtcDiagnosticTransaction, Join-DtcDiagnosticResourceManager, Receive-DtcDiagnosticTransact...
Manifest 2.0.0.0 NetAdapter {Disable-NetAdapter, Disable-NetAdapterBinding, Disable-NetAdapterChecksumOffload, Disable-NetAdapterEncapsulatedPacketTaskOffload...
Manifest 1.0.0.0 NetConnection {Get-NetConnectionProfile, Set-NetConnectionProfile}
Manifest 1.0.0.0 NetDiagnostics Get-NetView
Manifest 1.0.0.0 NetEventPacketCapture {New-NetEventSession, Remove-NetEventSession, Get-NetEventSession, Set-NetEventSession...}
Manifest 2.0.0.0 NetLbfo {Add-NetLbfoTeamMember, Add-NetLbfoTeamNic, Get-NetLbfoTeam, Get-NetLbfoTeamMember...}
Manifest 1.0.0.0 NetNat {Get-NetNat, Get-NetNatExternalAddress, Get-NetNatStaticMapping, Get-NetNatSession...}
Manifest 2.0.0.0 NetQos {Get-NetQosPolicy, Set-NetQosPolicy, Remove-NetQosPolicy, New-NetQosPolicy}
Manifest 2.0.0.0 NetSecurity {Get-DAPolicyChange, New-NetIPsecAuthProposal, New-NetIPsecMainModeCryptoProposal, New-NetIPsecQuickModeCryptoProposal...}
Manifest 1.0.0.0 NetSwitchTeam {New-NetSwitchTeam, Remove-NetSwitchTeam, Get-NetSwitchTeam, Rename-NetSwitchTeam...}
Manifest 1.0.0.0 NetTCPIP {Get-NetIPAddress, Get-NetIPInterface, Get-NetIPv4Protocol, Get-NetIPv6Protocol...}
Manifest 1.0.0.0 NetworkConnectivityStatus {Get-DAConnectionStatus, Get-NCSIPolicyConfiguration, Reset-NCSIPolicyConfiguration, Set-NCSIPolicyConfiguration}
Manifest 1.0.0.0 NetworkSwitchManager {Disable-NetworkSwitchEthernetPort, Enable-NetworkSwitchEthernetPort, Get-NetworkSwitchEthernetPort, Remove-NetworkSwitchEthernetP...
Manifest 1.0.0.0 NetworkTransition {Add-NetIPHttpsCertBinding, Disable-NetDnsTransitionConfiguration, Disable-NetIPHttpsProfile, Disable-NetNatTransitionConfiguratio...
Manifest 1.0.0.0 PcsvDevice {Get-PcsvDevice, Start-PcsvDevice, Stop-PcsvDevice, Restart-PcsvDevice...}
Binary 1.0.0.0 PersistentMemory {Get-PmemDisk, Get-PmemPhysicalDevice, Get-PmemUnusedRegion, New-PmemDisk...}
Manifest 1.0.0.0 PKI {Add-CertificateEnrollmentPolicyServer, Export-Certificate, Export-PfxCertificate, Get-CertificateAutoEnrollmentPolicy...}
Manifest 1.0.0.0 PnpDevice {Get-PnpDevice, Get-PnpDeviceProperty, Enable-PnpDevice, Disable-PnpDevice}
Manifest 1.1 PrintManagement {Add-Printer, Add-PrinterDriver, Add-PrinterPort, Get-PrintConfiguration...}
Binary 1.0.11 ProcessMitigations {Get-ProcessMitigation, Set-ProcessMitigation, ConvertTo-ProcessMitigationPolicy}
Script 3.0 Provisioning {Install-ProvisioningPackage, Export-ProvisioningPackage, Install-TrustedProvisioningCertificate, Export-Trace...}
Manifest 1.1 PSDesiredStateConfiguration {Set-DscLocalConfigurationManager, Start-DscConfiguration, Test-DscConfiguration, Publish-DscConfiguration...}
Script 1.0.0.0 PSDiagnostics {Disable-PSTrace, Disable-PSWSManCombinedTrace, Disable-WSManTrace, Enable-PSTrace...}
Binary 1.1.0.0 PSScheduledJob {New-JobTrigger, Add-JobTrigger, Remove-JobTrigger, Get-JobTrigger...}
Manifest 2.0.0.0 PSWorkflow {New-PSWorkflowExecutionOption, New-PSWorkflowSession, nwsn}
Manifest 1.0.0.0 PSWorkflowUtility Invoke-AsWorkflow
Manifest 1.0.0.0 ScheduledTasks {Get-ScheduledTask, Set-ScheduledTask, Register-ScheduledTask, Unregister-ScheduledTask...}
Manifest 2.0.0.0 SecureBoot {Confirm-SecureBootUEFI, Set-SecureBootUEFI, Get-SecureBootUEFI, Format-SecureBootUEFI...}
Manifest 2.0.0.0 SmbShare {Get-SmbShare, Remove-SmbShare, Set-SmbShare, Block-SmbShareAccess...}
Manifest 2.0.0.0 SmbWitness {Get-SmbWitnessClient, Move-SmbWitnessClient, gsmbw, msmbw...}
Manifest 1.0.0.0 StartLayout {Export-StartLayout, Import-StartLayout, Export-StartLayoutEdgeAssets, Get-StartApps}
Manifest 2.0.0.0 Storage {Add-InitiatorIdToMaskingSet, Add-PartitionAccessPath, Add-PhysicalDisk, Add-StorageFaultDomain...}
Manifest 1.0.0.0 StorageBusCache {Clear-StorageBusDisk, Disable-StorageBusCache, Disable-StorageBusDisk, Enable-StorageBusCache...}
Manifest 2.0.0.0 TLS {New-TlsSessionTicketKey, Enable-TlsSessionTicketKey, Disable-TlsSessionTicketKey, Export-TlsSessionTicketKey...}
Manifest 1.0.0.0 TroubleshootingPack {Get-TroubleshootingPack, Invoke-TroubleshootingPack}
Manifest 2.0.0.0 TrustedPlatformModule {Get-Tpm, Initialize-Tpm, Clear-Tpm, Unblock-Tpm...}
Binary 2.1.639.0 UEV {Clear-UevConfiguration, Clear-UevAppxPackage, Restore-UevBackup, Set-UevTemplateProfile...}
Manifest 2.0.0.0 VpnClient {Add-VpnConnection, Set-VpnConnection, Remove-VpnConnection, Get-VpnConnection...}
Manifest 1.0.0.0 Wdac {Get-OdbcDriver, Set-OdbcDriver, Get-OdbcDsn, Add-OdbcDsn...}
Manifest 2.0.0.0 Whea {Get-WheaMemoryPolicy, Set-WheaMemoryPolicy}
Manifest 1.0.0.0 WindowsDeveloperLicense {Get-WindowsDeveloperLicense, Unregister-WindowsDeveloperLicense, Show-WindowsDeveloperLicenseRegistration}
Script 1.0 WindowsErrorReporting {Enable-WindowsErrorReporting, Disable-WindowsErrorReporting, Get-WindowsErrorReporting}
Manifest 1.0.0.0 WindowsSearch {Get-WindowsSearchSetting, Set-WindowsSearchSetting}
Manifest 1.0.0.0 WindowsUpdate Get-WindowsUpdateLog
Manifest 1.0.0.2 WindowsUpdateProvider {Get-WUAVersion, Get-WULastInstallationDate, Get-WULastScanSuccessDate, Get-WUIsPendingReboot...}
ディレクトリ: C:\Program Files (x86)\Microsoft Azure Information Protection\Powershell
ModuleType Version Name ExportedCommands
---------- ------- ---- ----------------
Binary 1.48.204.0 AzureInformationProtection {Clear-RMSAuthentication, Get-RMSFileStatus, Get-RMSServer, Get-RMSServerAuthentication...}
ディレクトリ: C:\Program Files\Microsoft Message Analyzer\PowerShell
ModuleType Version Name ExportedCommands
---------- ------- ---- ----------------
Script 1.1.0.0 PEF
## Debug output
PS C:\Users\koyasuda> New-AzVmss -ResourceGroupName $rgname -Name $scaleSetName -VirtualMachineScaleSet $vmssConfig -Debug
デバッグ: 15:28:41 - NewAzureRmVmss begin processing with ParameterSet 'DefaultParameter'.
デバッグ: 15:28:42 - using account id 'koyasuda@microsoft.com'...
デバッグ: [Common.Authentication]: Authenticating using Account: 'koyasuda@microsoft.com', environment: 'AzureCloud', tenant: '72f988bf-86f1-41af-91ab-2d7cd011db47'
デバッグ: [Common.Authentication]: Authenticating using configuration values: Domain: '72f988bf-86f1-41af-91ab-2d7cd011db47', Endpoint: 'https://login.microsoftonline.com/', ClientId: '1950a258-22
7b-4e31-a9cf-717495945fc2', ClientRedirect: 'urn:ietf:wg:oauth:2.0:oob', ResourceClientUri: 'https://management.core.windows.net/', ValidateAuthority: 'True'
デバッグ: [Common.Authentication]: Acquiring token using context with Authority 'https://login.microsoftonline.com/72f988bf-86f1-41af-91ab-2d7cd011db47/', CorrelationId: '00000000-0000-0000-0000-0
00000000000', ValidateAuthority: 'True'
デバッグ: [Common.Authentication]: Acquiring token using AdalConfiguration with Domain: '72f988bf-86f1-41af-91ab-2d7cd011db47', AdEndpoint: 'https://login.microsoftonline.com/', ClientId: '1950a25
8-227b-4e31-a9cf-717495945fc2', ClientRedirectUri: urn:ietf:wg:oauth:2.0:oob
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7699887Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: ADAL PCL.Desktop with assembly version '3.19.2.6005', file version '3.19.50302.01
30' and informational version '2a8bec6c4c76d0c1ef819b55bdc3cda2d2605056' is running...
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7699887Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: ADAL PCL.Desktop with assembly version '3.19.2.6005', file version '3.19.50302.01
30' and informational version '2a8bec6c4c76d0c1ef819b55bdc3cda2d2605056' is running...
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7699887Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: === Token Acquisition started:
CacheType: null
Authentication Target: User
, Authority Host: login.microsoftonline.com
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7699887Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: === Token Acquisition started:
Authority: https://login.microsoftonline.com/72f988bf-86f1-41af-91ab-2d7cd011db47/
Resource: https://management.core.windows.net/
ClientId: 1950a258-227b-4e31-a9cf-717495945fc2
CacheType: null
Authentication Target: User
デバッグ: [ADAL]: Verbose: 2020-03-06T06:28:43.7709889Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: Loading from cache.
デバッグ: [ADAL]: Verbose: 2020-03-06T06:28:43.7709889Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: Loading from cache.
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7879915Z: 00000000-0000-0000-0000-000000000000 - LoggerBase.cs: Deserialized 9 items to token cache.
デバッグ: [ADAL]: Verbose: 2020-03-06T06:28:43.7879915Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: Looking up cache for a token...
デバッグ: [ADAL]: Verbose: 2020-03-06T06:28:43.7879915Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: Looking up cache for a token...
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7879915Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: An item matching the requested resource was found in the cache
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7879915Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: An item matching the requested resource was found in the cache
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7879915Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: 30.374633475 minutes left until token in cache expires
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7879915Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: 30.374633475 minutes left until token in cache expires
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7879915Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: A matching item (access token or refresh token or both) was found in the cache
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7879915Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: A matching item (access token or refresh token or both) was found in the cache
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7879915Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: === Token Acquisition finished successfully. An access token was returned: Expira
tion Time: 2020/03/06 6:59:06 +00:00
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7879915Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: === Token Acquisition finished successfully. An access token was returned: Expira
tion Time: 2020/03/06 6:59:06 +00:00Access Token Hash: xN5sWUNlFJ8Lh2a/vL9AFQQNkQb2kV2mhuU7rZ76G/k=
User id: 02261c1a-a7c9-45e8-a9b1-f4566190575b
デバッグ: [Common.Authentication]: Renewing Token with Type: 'Bearer', Expiry: '03/06/2020 06:59:06 +00:00', MultipleResource? 'True', Tenant: '72f988bf-86f1-41af-91ab-2d7cd011db47', UserId: 'koya
suda@microsoft.com'
デバッグ: [Common.Authentication]: User info for token DisplayId: 'koyasuda@microsoft.com', Name: Koya Yasuda, IdProvider: 'https://sts.windows.net/72f988bf-86f1-41af-91ab-2d7cd011db47/', Uid: '02
261c1a-a7c9-45e8-a9b1-f4566190575b'
デバッグ: [Common.Authentication]: Checking token expiration, token expires '03/06/2020 06:59:06 +00:00' Comparing to '03/06/2020 06:28:43 +00:00' With threshold '00:05:00', calculated time until
token expiry: '00:30:22.4514971'
デバッグ: ============================ HTTP REQUEST ============================
HTTP Method:
PUT
Absolute Uri:
https://management.azure.com/subscriptions/8aa22af4-9dad-44a9-8659-0a6884482967/resourceGroups/TestAppGW/providers/Microsoft.Compute/virtualMachineScaleSets/testuser?api-version=2019-07-01
Headers:
x-ms-client-request-id : a2692051-5d59-4813-9d69-f1af757e554e
accept-language : en-US
Body:
{
"sku": {
"name": "Standard_DS2_v2",
"capacity": 2
},
"properties": {
"upgradePolicy": {
"mode": "Automatic",
"automaticOSUpgradePolicy": {
"enableAutomaticOSUpgrade": false
}
},
"automaticRepairsPolicy": {
"enabled": false
},
"virtualMachineProfile": {
"osProfile": {
"computerNamePrefix": "testuser",
"adminUsername": "testuser",
"adminPassword": "AzureUser123"
},
"storageProfile": {
"imageReference": {
"id": "/subscriptions/8aa22af4-9dad-44a9-8659-0a6884482967/resourceGroups/0725/providers/Microsoft.Compute/images/image-image-20200210164408"
},
"osDisk": {
"writeAcceleratorEnabled": false,
"createOption": "FromImage"
}
},
"networkProfile": {
"networkInterfaceConfigurations": [
{
"name": "NetConfig",
"properties": {
"primary": true,
"enableAcceleratedNetworking": false,
"enableIPForwarding": false
}
}
]
}
}
},
"zones": [
"1",
"2",
"3"
],
"location": "japaneast",
"tags": {}
}
デバッグ: ============================ HTTP RESPONSE ============================
Status Code:
BadRequest
Headers:
Pragma : no-cache
x-ms-ratelimit-remaining-resource: Microsoft.Compute/CreateVMScaleSet3Min;59,Microsoft.Compute/CreateVMScaleSet30Min;299
Strict-Transport-Security : max-age=31536000; includeSubDomains
x-ms-request-id : 293aee18-4ac1-4d36-982a-c174a30234da
Cache-Control : no-cache
Server : Microsoft-HTTPAPI/2.0,Microsoft-HTTPAPI/2.0
x-ms-ratelimit-remaining-subscription-writes: 1199
x-ms-correlation-request-id : 874e72df-1662-4102-afa1-97e755a006cd
x-ms-routing-request-id : EASTASIA:20200306T062847Z:874e72df-1662-4102-afa1-97e755a006cd
X-Content-Type-Options : nosniff
Date : Fri, 06 Mar 2020 06:28:46 GMT
Body:
{
"error": {
"code": "BadRequest",
"message": "Automatic repairs feature on Virtual Machine Scale Set is supported when singlePlacementGroup is enabled."
}
}
デバッグ: AzureQoSEvent: CommandName - New-AzVmss; IsSuccess - True; Duration - 00:00:06.5790828;
デバッグ: Finish sending metric.
デバッグ: 15:28:48 - NewAzureRmVmss end processing.
New-AzVmss : Automatic repairs feature on Virtual Machine Scale Set is supported when singlePlacementGroup is enabled.
ErrorCode: BadRequest
ErrorMessage: Automatic repairs feature on Virtual Machine Scale Set is supported when singlePlacementGroup is enabled.
ErrorTarget:
StatusCode: 400
ReasonPhrase: Bad Request
OperationID : 293aee18-4ac1-4d36-982a-c174a30234da
発生場所 行:1 文字:1
+ New-AzVmss -ResourceGroupName $rgname -Name $scaleSetName -VirtualMac ...
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : CloseError: (:) [New-AzVmss]、ComputeCloudException
+ FullyQualifiedErrorId : Microsoft.Azure.Commands.Compute.Automation.NewAzureRmVmss
デバッグ: AzureQoSEvent: CommandName - New-AzVmss; IsSuccess - False; Duration - 00:00:06.5790828;; Exception - Microsoft.Azure.Commands.Compute.Common.ComputeCloudException: Automatic repairs fea
ture on Virtual Machine Scale Set is supported when singlePlacementGroup is enabled.
ErrorCode: BadRequest
ErrorMessage: Automatic repairs feature on Virtual Machine Scale Set is supported when singlePlacementGroup is enabled.
ErrorTarget:
StatusCode: 400
ReasonPhrase: Bad Request
OperationID : 293aee18-4ac1-4d36-982a-c174a30234da ---> Microsoft.Rest.Azure.CloudException: Automatic repairs feature on Virtual Machine Scale Set is supported when singlePlacementGroup is en
abled.
場所 Microsoft.Azure.Management.Compute.VirtualMachineScaleSetsOperations.<BeginCreateOrUpdateWithHttpMessagesAsync>d__26.MoveNext()
--- 直前に例外がスローされた場所からのスタック トレースの終わり ---
場所 System.Runtime.ExceptionServices.ExceptionDispatchInfo.Throw()
場所 System.Runtime.CompilerServices.TaskAwaiter.HandleNonSuccessAndDebuggerNotification(Task task)
場所 System.Runtime.CompilerServices.ConfiguredTaskAwaitable`1.ConfiguredTaskAwaiter.GetResult()
場所 Microsoft.Azure.Management.Compute.VirtualMachineScaleSetsOperations.<CreateOrUpdateWithHttpMessagesAsync>d__5.MoveNext()
--- 直前に例外がスローされた場所からのスタック トレースの終わり ---
場所 System.Runtime.ExceptionServices.ExceptionDispatchInfo.Throw()
場所 System.Runtime.CompilerServices.TaskAwaiter.HandleNonSuccessAndDebuggerNotification(Task task)
場所 System.Runtime.CompilerServices.ConfiguredTaskAwaitable`1.ConfiguredTaskAwaiter.GetResult()
場所 Microsoft.Azure.Management.Compute.VirtualMachineScaleSetsOperationsExtensions.<CreateOrUpdateAsync>d__1.MoveNext()
--- 直前に例外がスローされた場所からのスタック トレースの終わり ---
場所 System.Runtime.ExceptionServices.ExceptionDispatchInfo.Throw()
場所 System.Runtime.CompilerServices.TaskAwaiter.HandleNonSuccessAndDebuggerNotification(Task task)
場所 System.Runtime.CompilerServices.TaskAwaiter`1.GetResult()
場所 Microsoft.Azure.Management.Compute.VirtualMachineScaleSetsOperationsExtensions.CreateOrUpdate(IVirtualMachineScaleSetsOperations operations, String resourceGroupName, String vmScaleSetNa
me, VirtualMachineScaleSet parameters)
場所 Microsoft.Azure.Commands.Compute.Automation.NewAzureRmVmss.<ExecuteCmdlet>b__1_0()
場所 Microsoft.Azure.Commands.Compute.ComputeClientBaseCmdlet.ExecuteClientAction(Action action)
--- 内部例外スタック トレースの終わり ---
場所 Microsoft.Azure.Commands.Compute.ComputeClientBaseCmdlet.ExecuteClientAction(Action action)
場所 Microsoft.WindowsAzure.Commands.Utilities.Common.AzurePSCmdlet.ProcessRecord();
デバッグ: Finish sending metric.
デバッグ: 15:28:51 - NewAzureRmVmss end processing.
PS C:\Users\koyasuda>
## Error output
PS C:\Users\koyasuda> Resolve-AzError
警告: Breaking changes in the cmdlet 'Resolve-AzError' :
警告: - The `Resolve-Error` alias will be removed in a future release. Please change any scripts that use this alias to use `Resolve-AzError` instead.
警告: NOTE : Go to https://aka.ms/azps-changewarnings for steps to suppress this breaking change warning, and other information on breaking changes in Azure PowerShell.
HistoryId: 5
RequestId :
Message : Automatic repairs feature on Virtual Machine Scale Set is supported when singlePlacementGroup is enabled.
ErrorCode: BadRequest
ErrorMessage: Automatic repairs feature on Virtual Machine Scale Set is supported when singlePlacementGroup is enabled.
ErrorTarget:
StatusCode: 400
ReasonPhrase: Bad Request
OperationID : 293aee18-4ac1-4d36-982a-c174a30234da
ServerMessage :
ServerResponse :
RequestMessage :
InvocationInfo : {New-AzVmss}
Line : New-AzVmss -ResourceGroupName $rgname -Name $scaleSetName -VirtualMachineScaleSet $vmssConfig -Debug
Position : 発生場所 行:1 文字:1
+ New-AzVmss -ResourceGroupName $rgname -Name $scaleSetName -VirtualMac ...
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
StackTrace : 場所 Microsoft.Azure.Commands.Compute.ComputeClientBaseCmdlet.ExecuteClientAction(Action action)
場所 Microsoft.WindowsAzure.Commands.Utilities.Common.AzurePSCmdlet.ProcessRecord()
HistoryId : 5
HistoryId: 2
RequestId :
Message : Automatic repairs feature on Virtual Machine Scale Set is supported when singlePlacementGroup is enabled.
ErrorCode: BadRequest
ErrorMessage: Automatic repairs feature on Virtual Machine Scale Set is supported when singlePlacementGroup is enabled.
ErrorTarget:
StatusCode: 400
ReasonPhrase: Bad Request
OperationID : 6f46d687-7ce4-45d4-8e51-62316780cb4b
ServerMessage :
ServerResponse :
RequestMessage :
InvocationInfo : {New-AzVmss}
Line : New-AzVmss `
Position : 発生場所 行:24 文字:1
+ New-AzVmss `
+ ~~~~~~~~~~~~
StackTrace : 場所 Microsoft.Azure.Commands.Compute.ComputeClientBaseCmdlet.ExecuteClientAction(Action action)
場所 Microsoft.WindowsAzure.Commands.Utilities.Common.AzurePSCmdlet.ProcessRecord()
HistoryId : 2
| 1.0 | We will be required to enable singlePlacementGroup even though you have not enabled AutomaticRepairsPolicy when we deploying VMSS using New-AzVmss. -
## Description
When we deploy new VMSS under APPGW whose health prove is enabled, the error message is occurred.
I don't choose " -EnableAutomaticRepair " option in "New-AzVmssConfig".
However, the error message tells me that you should enable "singlePlacementGroup" to deply VMSS.
When I tried in Ver Az 1.1.0, same error is not occurred.
I and Cx confirmed that same error is occurred in Az 3.5.0 and 3.1.0.
I think that this reason is "Automatic repairs feature" is newer function.
PS C:\Users\koyasuda> Get-InstalledModule -Name Az -AllVersions | select Name,Version
Name Version
---- -------
Az 1.1.0
Az 3.5.0
when I deployed single VMSS(not under APPGW), the same error is not occurred.
## Steps to reproduce
I attached my scripts.
==========================
$vnet = Get-AzVirtualNetwork `
-ResourceGroupName $rgname `
-Name $vnet.Name
$appgw = Get-AzApplicationGateway `
-ResourceGroupName $rgname `
-Name $appgwName
$backendPool = Get-AzApplicationGatewayBackendAddressPool `
-Name $defaultPool.Name `
-ApplicationGateway $appgw
$ipConfig = New-AzVmssIpConfig `
-Name $gipconfig.Name `
-SubnetId $vnet.Subnets[0].Id `
-ApplicationGatewayBackendAddressPoolsId $backendPool.Id
$vmssConfig = New-AzVmssConfig `
-Location japaneast `
-SkuCapacity 2 `
-SkuName Standard_DS2_v2 `
-UpgradePolicyMode Automatic `
-Zone @("1", "2", "3")
$vmImage = Get-AzImage -ResourceGroupName $rgname -ImageName $vmImageName
Set-AzVmssStorageProfile $vmssConfig -ImageReferenceId $vmImage.Id -OsDiskCreateOption "FromImage"
Set-AzVmssOsProfile $vmssConfig `
-AdminUsername $vmssAdminUserName `
-AdminPassword $vmssAdminPassword `
-ComputerNamePrefix $scaleSetName
Add-AzVmssNetworkInterfaceConfiguration `
-VirtualMachineScaleSet $vmssConfig `
-Name "NetConfig" `
-Primary $true `
-IPConfiguration $ipConfig
New-AzVmss -ResourceGroupName $rgname -Name $scaleSetName -VirtualMachineScaleSet $vmssConfig -Debug
==========================
## Environment data
PS C:\Users\koyasuda> $PSVersionTable
Name Value
---- -----
PSVersion 5.1.18362.628
PSEdition Desktop
PSCompatibleVersions {1.0, 2.0, 3.0, 4.0...}
BuildVersion 10.0.18362.628
CLRVersion 4.0.30319.42000
WSManStackVersion 3.0
PSRemotingProtocolVersion 2.3
SerializationVersion 1.1.0.1
## Module versions
<!-- Please run (Get-Module -ListAvailable) and paste the output in the below code block -->
ModuleType Version Name ExportedCommands
---------- ------- ---- ----------------
Manifest 1.0.0.0 AppBackgroundTask {Disable-AppBackgroundTaskDiagnosticLog, Enable-AppBackgroundTaskDiagnosticLog, Set-AppBackgroundTaskResourcePolicy, Unregister-Ap...
Manifest 2.0.0.0 AppLocker {Get-AppLockerFileInformation, Get-AppLockerPolicy, New-AppLockerPolicy, Set-AppLockerPolicy...}
Manifest 1.0.0.0 AppvClient {Add-AppvClientConnectionGroup, Add-AppvClientPackage, Add-AppvPublishingServer, Disable-Appv...}
Manifest 2.0.1.0 Appx {Add-AppxPackage, Get-AppxPackage, Get-AppxPackageManifest, Remove-AppxPackage...}
Script 1.0.0.0 AssignedAccess {Clear-AssignedAccess, Get-AssignedAccess, Set-AssignedAccess}
Manifest 1.0.0.0 BitLocker {Unlock-BitLocker, Suspend-BitLocker, Resume-BitLocker, Remove-BitLockerKeyProtector...}
Manifest 2.0.0.0 BitsTransfer {Add-BitsFile, Complete-BitsTransfer, Get-BitsTransfer, Remove-BitsTransfer...}
Manifest 1.0.0.0 BranchCache {Add-BCDataCacheExtension, Clear-BCCache, Disable-BC, Disable-BCDowngrading...}
Manifest 1.0.0.0 CimCmdlets {Get-CimAssociatedInstance, Get-CimClass, Get-CimInstance, Get-CimSession...}
Manifest 1.0 ConfigCI {Get-SystemDriver, New-CIPolicyRule, New-CIPolicy, Get-CIPolicy...}
Manifest 1.0 ConfigDefender {Get-MpPreference, Set-MpPreference, Add-MpPreference, Remove-MpPreference...}
Manifest 1.0 Defender {Get-MpPreference, Set-MpPreference, Add-MpPreference, Remove-MpPreference...}
Manifest 1.0.2.0 DeliveryOptimization {Delete-DeliveryOptimizationCache, Get-DeliveryOptimizationStatus, Set-DeliveryOptimizationStatus, Get-DeliveryOptimizationPerfSna...
Manifest 1.0.0.0 DirectAccessClientComponents {Disable-DAManualEntryPointSelection, Enable-DAManualEntryPointSelection, Get-DAClientExperienceConfiguration, Get-DAEntryPointTab...
Script 3.0 Dism {Add-AppxProvisionedPackage, Add-WindowsDriver, Add-WindowsCapability, Add-WindowsImage...}
Manifest 1.0.0.0 DnsClient {Resolve-DnsName, Clear-DnsClientCache, Get-DnsClient, Get-DnsClientCache...}
Manifest 1.0.0.0 EventTracingManagement {Start-EtwTraceSession, New-EtwTraceSession, Get-EtwTraceSession, Update-EtwTraceSession...}
Manifest 1.0.0.0 HgsClient {Get-HgsAttestationBaselinePolicy, Get-HgsClientConfiguration, Test-HgsClientConfiguration, Set-HgsClientConfiguration...}
Manifest 1.0.0.0 HgsDiagnostics {New-HgsTraceTarget, Get-HgsTrace, Get-HgsTraceFileData, Test-HgsTraceTarget}
Manifest 1.0.0.1 HostNetworkingService {Remove-HnsNamespace, Remove-HnsEndpoint, Get-HnsEndpoint, Get-HnsNamespace...}
Binary 2.0.0.0 Hyper-V {Add-VMAssignableDevice, Add-VMDvdDrive, Add-VMFibreChannelHba, Add-VMGpuPartitionAdapter...}
Binary 1.1 Hyper-V {Add-VMDvdDrive, Add-VMFibreChannelHba, Add-VMHardDiskDrive, Add-VMMigrationNetwork...}
Manifest 2.0.0.0 International {Get-WinDefaultInputMethodOverride, Set-WinDefaultInputMethodOverride, Get-WinHomeLocation, Set-WinHomeLocation...}
Manifest 1.0.0.0 iSCSI {Get-IscsiTargetPortal, New-IscsiTargetPortal, Remove-IscsiTargetPortal, Update-IscsiTargetPortal...}
Script 1.0.0.0 ISE {New-IseSnippet, Import-IseSnippet, Get-IseSnippet}
Manifest 1.0.0.0 Kds {Add-KdsRootKey, Get-KdsRootKey, Test-KdsRootKey, Set-KdsConfiguration...}
Manifest 1.0.1.0 Microsoft.PowerShell.Archive {Compress-Archive, Expand-Archive}
Manifest 3.0.0.0 Microsoft.PowerShell.Diagnostics {Get-WinEvent, Get-Counter, Import-Counter, Export-Counter...}
Manifest 3.0.0.0 Microsoft.PowerShell.Host {Start-Transcript, Stop-Transcript}
Manifest 1.0.0.0 Microsoft.PowerShell.LocalAccounts {Add-LocalGroupMember, Disable-LocalUser, Enable-LocalUser, Get-LocalGroup...}
Manifest 3.1.0.0 Microsoft.PowerShell.Management {Add-Content, Clear-Content, Clear-ItemProperty, Join-Path...}
Script 1.0 Microsoft.PowerShell.ODataUtils Export-ODataEndpointProxy
Manifest 3.0.0.0 Microsoft.PowerShell.Security {Get-Acl, Set-Acl, Get-PfxCertificate, Get-Credential...}
Manifest 3.1.0.0 Microsoft.PowerShell.Utility {Format-List, Format-Custom, Format-Table, Format-Wide...}
Manifest 3.0.0.0 Microsoft.WSMan.Management {Disable-WSManCredSSP, Enable-WSManCredSSP, Get-WSManCredSSP, Set-WSManQuickConfig...}
Manifest 1.0 MMAgent {Disable-MMAgent, Enable-MMAgent, Set-MMAgent, Get-MMAgent...}
Manifest 1.0.0.0 MsDtc {New-DtcDiagnosticTransaction, Complete-DtcDiagnosticTransaction, Join-DtcDiagnosticResourceManager, Receive-DtcDiagnosticTransact...
Manifest 2.0.0.0 NetAdapter {Disable-NetAdapter, Disable-NetAdapterBinding, Disable-NetAdapterChecksumOffload, Disable-NetAdapterEncapsulatedPacketTaskOffload...
Manifest 1.0.0.0 NetConnection {Get-NetConnectionProfile, Set-NetConnectionProfile}
Manifest 1.0.0.0 NetDiagnostics Get-NetView
Manifest 1.0.0.0 NetEventPacketCapture {New-NetEventSession, Remove-NetEventSession, Get-NetEventSession, Set-NetEventSession...}
Manifest 2.0.0.0 NetLbfo {Add-NetLbfoTeamMember, Add-NetLbfoTeamNic, Get-NetLbfoTeam, Get-NetLbfoTeamMember...}
Manifest 1.0.0.0 NetNat {Get-NetNat, Get-NetNatExternalAddress, Get-NetNatStaticMapping, Get-NetNatSession...}
Manifest 2.0.0.0 NetQos {Get-NetQosPolicy, Set-NetQosPolicy, Remove-NetQosPolicy, New-NetQosPolicy}
Manifest 2.0.0.0 NetSecurity {Get-DAPolicyChange, New-NetIPsecAuthProposal, New-NetIPsecMainModeCryptoProposal, New-NetIPsecQuickModeCryptoProposal...}
Manifest 1.0.0.0 NetSwitchTeam {New-NetSwitchTeam, Remove-NetSwitchTeam, Get-NetSwitchTeam, Rename-NetSwitchTeam...}
Manifest 1.0.0.0 NetTCPIP {Get-NetIPAddress, Get-NetIPInterface, Get-NetIPv4Protocol, Get-NetIPv6Protocol...}
Manifest 1.0.0.0 NetworkConnectivityStatus {Get-DAConnectionStatus, Get-NCSIPolicyConfiguration, Reset-NCSIPolicyConfiguration, Set-NCSIPolicyConfiguration}
Manifest 1.0.0.0 NetworkSwitchManager {Disable-NetworkSwitchEthernetPort, Enable-NetworkSwitchEthernetPort, Get-NetworkSwitchEthernetPort, Remove-NetworkSwitchEthernetP...
Manifest 1.0.0.0 NetworkTransition {Add-NetIPHttpsCertBinding, Disable-NetDnsTransitionConfiguration, Disable-NetIPHttpsProfile, Disable-NetNatTransitionConfiguratio...
Manifest 1.0.0.0 PcsvDevice {Get-PcsvDevice, Start-PcsvDevice, Stop-PcsvDevice, Restart-PcsvDevice...}
Binary 1.0.0.0 PersistentMemory {Get-PmemDisk, Get-PmemPhysicalDevice, Get-PmemUnusedRegion, New-PmemDisk...}
Manifest 1.0.0.0 PKI {Add-CertificateEnrollmentPolicyServer, Export-Certificate, Export-PfxCertificate, Get-CertificateAutoEnrollmentPolicy...}
Manifest 1.0.0.0 PnpDevice {Get-PnpDevice, Get-PnpDeviceProperty, Enable-PnpDevice, Disable-PnpDevice}
Manifest 1.1 PrintManagement {Add-Printer, Add-PrinterDriver, Add-PrinterPort, Get-PrintConfiguration...}
Binary 1.0.11 ProcessMitigations {Get-ProcessMitigation, Set-ProcessMitigation, ConvertTo-ProcessMitigationPolicy}
Script 3.0 Provisioning {Install-ProvisioningPackage, Export-ProvisioningPackage, Install-TrustedProvisioningCertificate, Export-Trace...}
Manifest 1.1 PSDesiredStateConfiguration {Set-DscLocalConfigurationManager, Start-DscConfiguration, Test-DscConfiguration, Publish-DscConfiguration...}
Script 1.0.0.0 PSDiagnostics {Disable-PSTrace, Disable-PSWSManCombinedTrace, Disable-WSManTrace, Enable-PSTrace...}
Binary 1.1.0.0 PSScheduledJob {New-JobTrigger, Add-JobTrigger, Remove-JobTrigger, Get-JobTrigger...}
Manifest 2.0.0.0 PSWorkflow {New-PSWorkflowExecutionOption, New-PSWorkflowSession, nwsn}
Manifest 1.0.0.0 PSWorkflowUtility Invoke-AsWorkflow
Manifest 1.0.0.0 ScheduledTasks {Get-ScheduledTask, Set-ScheduledTask, Register-ScheduledTask, Unregister-ScheduledTask...}
Manifest 2.0.0.0 SecureBoot {Confirm-SecureBootUEFI, Set-SecureBootUEFI, Get-SecureBootUEFI, Format-SecureBootUEFI...}
Manifest 2.0.0.0 SmbShare {Get-SmbShare, Remove-SmbShare, Set-SmbShare, Block-SmbShareAccess...}
Manifest 2.0.0.0 SmbWitness {Get-SmbWitnessClient, Move-SmbWitnessClient, gsmbw, msmbw...}
Manifest 1.0.0.0 StartLayout {Export-StartLayout, Import-StartLayout, Export-StartLayoutEdgeAssets, Get-StartApps}
Manifest 2.0.0.0 Storage {Add-InitiatorIdToMaskingSet, Add-PartitionAccessPath, Add-PhysicalDisk, Add-StorageFaultDomain...}
Manifest 1.0.0.0 StorageBusCache {Clear-StorageBusDisk, Disable-StorageBusCache, Disable-StorageBusDisk, Enable-StorageBusCache...}
Manifest 2.0.0.0 TLS {New-TlsSessionTicketKey, Enable-TlsSessionTicketKey, Disable-TlsSessionTicketKey, Export-TlsSessionTicketKey...}
Manifest 1.0.0.0 TroubleshootingPack {Get-TroubleshootingPack, Invoke-TroubleshootingPack}
Manifest 2.0.0.0 TrustedPlatformModule {Get-Tpm, Initialize-Tpm, Clear-Tpm, Unblock-Tpm...}
Binary 2.1.639.0 UEV {Clear-UevConfiguration, Clear-UevAppxPackage, Restore-UevBackup, Set-UevTemplateProfile...}
Manifest 2.0.0.0 VpnClient {Add-VpnConnection, Set-VpnConnection, Remove-VpnConnection, Get-VpnConnection...}
Manifest 1.0.0.0 Wdac {Get-OdbcDriver, Set-OdbcDriver, Get-OdbcDsn, Add-OdbcDsn...}
Manifest 2.0.0.0 Whea {Get-WheaMemoryPolicy, Set-WheaMemoryPolicy}
Manifest 1.0.0.0 WindowsDeveloperLicense {Get-WindowsDeveloperLicense, Unregister-WindowsDeveloperLicense, Show-WindowsDeveloperLicenseRegistration}
Script 1.0 WindowsErrorReporting {Enable-WindowsErrorReporting, Disable-WindowsErrorReporting, Get-WindowsErrorReporting}
Manifest 1.0.0.0 WindowsSearch {Get-WindowsSearchSetting, Set-WindowsSearchSetting}
Manifest 1.0.0.0 WindowsUpdate Get-WindowsUpdateLog
Manifest 1.0.0.2 WindowsUpdateProvider {Get-WUAVersion, Get-WULastInstallationDate, Get-WULastScanSuccessDate, Get-WUIsPendingReboot...}
ディレクトリ: C:\Program Files (x86)\Microsoft Azure Information Protection\Powershell
ModuleType Version Name ExportedCommands
---------- ------- ---- ----------------
Binary 1.48.204.0 AzureInformationProtection {Clear-RMSAuthentication, Get-RMSFileStatus, Get-RMSServer, Get-RMSServerAuthentication...}
ディレクトリ: C:\Program Files\Microsoft Message Analyzer\PowerShell
ModuleType Version Name ExportedCommands
---------- ------- ---- ----------------
Script 1.1.0.0 PEF
## Debug output
PS C:\Users\koyasuda> New-AzVmss -ResourceGroupName $rgname -Name $scaleSetName -VirtualMachineScaleSet $vmssConfig -Debug
デバッグ: 15:28:41 - NewAzureRmVmss begin processing with ParameterSet 'DefaultParameter'.
デバッグ: 15:28:42 - using account id 'koyasuda@microsoft.com'...
デバッグ: [Common.Authentication]: Authenticating using Account: 'koyasuda@microsoft.com', environment: 'AzureCloud', tenant: '72f988bf-86f1-41af-91ab-2d7cd011db47'
デバッグ: [Common.Authentication]: Authenticating using configuration values: Domain: '72f988bf-86f1-41af-91ab-2d7cd011db47', Endpoint: 'https://login.microsoftonline.com/', ClientId: '1950a258-22
7b-4e31-a9cf-717495945fc2', ClientRedirect: 'urn:ietf:wg:oauth:2.0:oob', ResourceClientUri: 'https://management.core.windows.net/', ValidateAuthority: 'True'
デバッグ: [Common.Authentication]: Acquiring token using context with Authority 'https://login.microsoftonline.com/72f988bf-86f1-41af-91ab-2d7cd011db47/', CorrelationId: '00000000-0000-0000-0000-0
00000000000', ValidateAuthority: 'True'
デバッグ: [Common.Authentication]: Acquiring token using AdalConfiguration with Domain: '72f988bf-86f1-41af-91ab-2d7cd011db47', AdEndpoint: 'https://login.microsoftonline.com/', ClientId: '1950a25
8-227b-4e31-a9cf-717495945fc2', ClientRedirectUri: urn:ietf:wg:oauth:2.0:oob
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7699887Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: ADAL PCL.Desktop with assembly version '3.19.2.6005', file version '3.19.50302.01
30' and informational version '2a8bec6c4c76d0c1ef819b55bdc3cda2d2605056' is running...
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7699887Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: ADAL PCL.Desktop with assembly version '3.19.2.6005', file version '3.19.50302.01
30' and informational version '2a8bec6c4c76d0c1ef819b55bdc3cda2d2605056' is running...
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7699887Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: === Token Acquisition started:
CacheType: null
Authentication Target: User
, Authority Host: login.microsoftonline.com
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7699887Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: === Token Acquisition started:
Authority: https://login.microsoftonline.com/72f988bf-86f1-41af-91ab-2d7cd011db47/
Resource: https://management.core.windows.net/
ClientId: 1950a258-227b-4e31-a9cf-717495945fc2
CacheType: null
Authentication Target: User
デバッグ: [ADAL]: Verbose: 2020-03-06T06:28:43.7709889Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: Loading from cache.
デバッグ: [ADAL]: Verbose: 2020-03-06T06:28:43.7709889Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: Loading from cache.
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7879915Z: 00000000-0000-0000-0000-000000000000 - LoggerBase.cs: Deserialized 9 items to token cache.
デバッグ: [ADAL]: Verbose: 2020-03-06T06:28:43.7879915Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: Looking up cache for a token...
デバッグ: [ADAL]: Verbose: 2020-03-06T06:28:43.7879915Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: Looking up cache for a token...
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7879915Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: An item matching the requested resource was found in the cache
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7879915Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: An item matching the requested resource was found in the cache
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7879915Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: 30.374633475 minutes left until token in cache expires
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7879915Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: 30.374633475 minutes left until token in cache expires
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7879915Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: A matching item (access token or refresh token or both) was found in the cache
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7879915Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: A matching item (access token or refresh token or both) was found in the cache
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7879915Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: === Token Acquisition finished successfully. An access token was returned: Expira
tion Time: 2020/03/06 6:59:06 +00:00
デバッグ: [ADAL]: Information: 2020-03-06T06:28:43.7879915Z: bb3f137b-a90f-4123-bd92-e68ac323e69b - LoggerBase.cs: === Token Acquisition finished successfully. An access token was returned: Expira
tion Time: 2020/03/06 6:59:06 +00:00Access Token Hash: xN5sWUNlFJ8Lh2a/vL9AFQQNkQb2kV2mhuU7rZ76G/k=
User id: 02261c1a-a7c9-45e8-a9b1-f4566190575b
デバッグ: [Common.Authentication]: Renewing Token with Type: 'Bearer', Expiry: '03/06/2020 06:59:06 +00:00', MultipleResource? 'True', Tenant: '72f988bf-86f1-41af-91ab-2d7cd011db47', UserId: 'koya
suda@microsoft.com'
デバッグ: [Common.Authentication]: User info for token DisplayId: 'koyasuda@microsoft.com', Name: Koya Yasuda, IdProvider: 'https://sts.windows.net/72f988bf-86f1-41af-91ab-2d7cd011db47/', Uid: '02
261c1a-a7c9-45e8-a9b1-f4566190575b'
デバッグ: [Common.Authentication]: Checking token expiration, token expires '03/06/2020 06:59:06 +00:00' Comparing to '03/06/2020 06:28:43 +00:00' With threshold '00:05:00', calculated time until
token expiry: '00:30:22.4514971'
デバッグ: ============================ HTTP REQUEST ============================
HTTP Method:
PUT
Absolute Uri:
https://management.azure.com/subscriptions/8aa22af4-9dad-44a9-8659-0a6884482967/resourceGroups/TestAppGW/providers/Microsoft.Compute/virtualMachineScaleSets/testuser?api-version=2019-07-01
Headers:
x-ms-client-request-id : a2692051-5d59-4813-9d69-f1af757e554e
accept-language : en-US
Body:
{
"sku": {
"name": "Standard_DS2_v2",
"capacity": 2
},
"properties": {
"upgradePolicy": {
"mode": "Automatic",
"automaticOSUpgradePolicy": {
"enableAutomaticOSUpgrade": false
}
},
"automaticRepairsPolicy": {
"enabled": false
},
"virtualMachineProfile": {
"osProfile": {
"computerNamePrefix": "testuser",
"adminUsername": "testuser",
"adminPassword": "AzureUser123"
},
"storageProfile": {
"imageReference": {
"id": "/subscriptions/8aa22af4-9dad-44a9-8659-0a6884482967/resourceGroups/0725/providers/Microsoft.Compute/images/image-image-20200210164408"
},
"osDisk": {
"writeAcceleratorEnabled": false,
"createOption": "FromImage"
}
},
"networkProfile": {
"networkInterfaceConfigurations": [
{
"name": "NetConfig",
"properties": {
"primary": true,
"enableAcceleratedNetworking": false,
"enableIPForwarding": false
}
}
]
}
}
},
"zones": [
"1",
"2",
"3"
],
"location": "japaneast",
"tags": {}
}
デバッグ: ============================ HTTP RESPONSE ============================
Status Code:
BadRequest
Headers:
Pragma : no-cache
x-ms-ratelimit-remaining-resource: Microsoft.Compute/CreateVMScaleSet3Min;59,Microsoft.Compute/CreateVMScaleSet30Min;299
Strict-Transport-Security : max-age=31536000; includeSubDomains
x-ms-request-id : 293aee18-4ac1-4d36-982a-c174a30234da
Cache-Control : no-cache
Server : Microsoft-HTTPAPI/2.0,Microsoft-HTTPAPI/2.0
x-ms-ratelimit-remaining-subscription-writes: 1199
x-ms-correlation-request-id : 874e72df-1662-4102-afa1-97e755a006cd
x-ms-routing-request-id : EASTASIA:20200306T062847Z:874e72df-1662-4102-afa1-97e755a006cd
X-Content-Type-Options : nosniff
Date : Fri, 06 Mar 2020 06:28:46 GMT
Body:
{
"error": {
"code": "BadRequest",
"message": "Automatic repairs feature on Virtual Machine Scale Set is supported when singlePlacementGroup is enabled."
}
}
デバッグ: AzureQoSEvent: CommandName - New-AzVmss; IsSuccess - True; Duration - 00:00:06.5790828;
デバッグ: Finish sending metric.
デバッグ: 15:28:48 - NewAzureRmVmss end processing.
New-AzVmss : Automatic repairs feature on Virtual Machine Scale Set is supported when singlePlacementGroup is enabled.
ErrorCode: BadRequest
ErrorMessage: Automatic repairs feature on Virtual Machine Scale Set is supported when singlePlacementGroup is enabled.
ErrorTarget:
StatusCode: 400
ReasonPhrase: Bad Request
OperationID : 293aee18-4ac1-4d36-982a-c174a30234da
発生場所 行:1 文字:1
+ New-AzVmss -ResourceGroupName $rgname -Name $scaleSetName -VirtualMac ...
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : CloseError: (:) [New-AzVmss]、ComputeCloudException
+ FullyQualifiedErrorId : Microsoft.Azure.Commands.Compute.Automation.NewAzureRmVmss
デバッグ: AzureQoSEvent: CommandName - New-AzVmss; IsSuccess - False; Duration - 00:00:06.5790828;; Exception - Microsoft.Azure.Commands.Compute.Common.ComputeCloudException: Automatic repairs fea
ture on Virtual Machine Scale Set is supported when singlePlacementGroup is enabled.
ErrorCode: BadRequest
ErrorMessage: Automatic repairs feature on Virtual Machine Scale Set is supported when singlePlacementGroup is enabled.
ErrorTarget:
StatusCode: 400
ReasonPhrase: Bad Request
OperationID : 293aee18-4ac1-4d36-982a-c174a30234da ---> Microsoft.Rest.Azure.CloudException: Automatic repairs feature on Virtual Machine Scale Set is supported when singlePlacementGroup is en
abled.
場所 Microsoft.Azure.Management.Compute.VirtualMachineScaleSetsOperations.<BeginCreateOrUpdateWithHttpMessagesAsync>d__26.MoveNext()
--- 直前に例外がスローされた場所からのスタック トレースの終わり ---
場所 System.Runtime.ExceptionServices.ExceptionDispatchInfo.Throw()
場所 System.Runtime.CompilerServices.TaskAwaiter.HandleNonSuccessAndDebuggerNotification(Task task)
場所 System.Runtime.CompilerServices.ConfiguredTaskAwaitable`1.ConfiguredTaskAwaiter.GetResult()
場所 Microsoft.Azure.Management.Compute.VirtualMachineScaleSetsOperations.<CreateOrUpdateWithHttpMessagesAsync>d__5.MoveNext()
--- 直前に例外がスローされた場所からのスタック トレースの終わり ---
場所 System.Runtime.ExceptionServices.ExceptionDispatchInfo.Throw()
場所 System.Runtime.CompilerServices.TaskAwaiter.HandleNonSuccessAndDebuggerNotification(Task task)
場所 System.Runtime.CompilerServices.ConfiguredTaskAwaitable`1.ConfiguredTaskAwaiter.GetResult()
場所 Microsoft.Azure.Management.Compute.VirtualMachineScaleSetsOperationsExtensions.<CreateOrUpdateAsync>d__1.MoveNext()
--- 直前に例外がスローされた場所からのスタック トレースの終わり ---
場所 System.Runtime.ExceptionServices.ExceptionDispatchInfo.Throw()
場所 System.Runtime.CompilerServices.TaskAwaiter.HandleNonSuccessAndDebuggerNotification(Task task)
場所 System.Runtime.CompilerServices.TaskAwaiter`1.GetResult()
場所 Microsoft.Azure.Management.Compute.VirtualMachineScaleSetsOperationsExtensions.CreateOrUpdate(IVirtualMachineScaleSetsOperations operations, String resourceGroupName, String vmScaleSetNa
me, VirtualMachineScaleSet parameters)
場所 Microsoft.Azure.Commands.Compute.Automation.NewAzureRmVmss.<ExecuteCmdlet>b__1_0()
場所 Microsoft.Azure.Commands.Compute.ComputeClientBaseCmdlet.ExecuteClientAction(Action action)
--- 内部例外スタック トレースの終わり ---
場所 Microsoft.Azure.Commands.Compute.ComputeClientBaseCmdlet.ExecuteClientAction(Action action)
場所 Microsoft.WindowsAzure.Commands.Utilities.Common.AzurePSCmdlet.ProcessRecord();
デバッグ: Finish sending metric.
デバッグ: 15:28:51 - NewAzureRmVmss end processing.
PS C:\Users\koyasuda>
## Error output
PS C:\Users\koyasuda> Resolve-AzError
警告: Breaking changes in the cmdlet 'Resolve-AzError' :
警告: - The `Resolve-Error` alias will be removed in a future release. Please change any scripts that use this alias to use `Resolve-AzError` instead.
警告: NOTE : Go to https://aka.ms/azps-changewarnings for steps to suppress this breaking change warning, and other information on breaking changes in Azure PowerShell.
HistoryId: 5
RequestId :
Message : Automatic repairs feature on Virtual Machine Scale Set is supported when singlePlacementGroup is enabled.
ErrorCode: BadRequest
ErrorMessage: Automatic repairs feature on Virtual Machine Scale Set is supported when singlePlacementGroup is enabled.
ErrorTarget:
StatusCode: 400
ReasonPhrase: Bad Request
OperationID : 293aee18-4ac1-4d36-982a-c174a30234da
ServerMessage :
ServerResponse :
RequestMessage :
InvocationInfo : {New-AzVmss}
Line : New-AzVmss -ResourceGroupName $rgname -Name $scaleSetName -VirtualMachineScaleSet $vmssConfig -Debug
Position : 発生場所 行:1 文字:1
+ New-AzVmss -ResourceGroupName $rgname -Name $scaleSetName -VirtualMac ...
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
StackTrace : 場所 Microsoft.Azure.Commands.Compute.ComputeClientBaseCmdlet.ExecuteClientAction(Action action)
場所 Microsoft.WindowsAzure.Commands.Utilities.Common.AzurePSCmdlet.ProcessRecord()
HistoryId : 5
HistoryId: 2
RequestId :
Message : Automatic repairs feature on Virtual Machine Scale Set is supported when singlePlacementGroup is enabled.
ErrorCode: BadRequest
ErrorMessage: Automatic repairs feature on Virtual Machine Scale Set is supported when singlePlacementGroup is enabled.
ErrorTarget:
StatusCode: 400
ReasonPhrase: Bad Request
OperationID : 6f46d687-7ce4-45d4-8e51-62316780cb4b
ServerMessage :
ServerResponse :
RequestMessage :
InvocationInfo : {New-AzVmss}
Line : New-AzVmss `
Position : 発生場所 行:24 文字:1
+ New-AzVmss `
+ ~~~~~~~~~~~~
StackTrace : 場所 Microsoft.Azure.Commands.Compute.ComputeClientBaseCmdlet.ExecuteClientAction(Action action)
場所 Microsoft.WindowsAzure.Commands.Utilities.Common.AzurePSCmdlet.ProcessRecord()
HistoryId : 2
| non_defect | we will be required to enable singleplacementgroup even though you have not enabled automaticrepairspolicy when we deploying vmss using new azvmss description when we deploy new vmss under appgw whose health prove is enabled the error message is occurred i don t choose enableautomaticrepair option in new azvmssconfig however the error message tells me that you should enable singleplacementgroup to deply vmss when i tried in ver az same error is not occurred i and cx confirmed that same error is occurred in az and i think that this reason is automatic repairs feature is newer function ps c users koyasuda get installedmodule name az allversions select name version name version az az when i deployed single vmss not under appgw the same error is not occurred steps to reproduce i attached my scripts vnet get azvirtualnetwork resourcegroupname rgname name vnet name appgw get azapplicationgateway resourcegroupname rgname name appgwname backendpool get azapplicationgatewaybackendaddresspool name defaultpool name applicationgateway appgw ipconfig new azvmssipconfig name gipconfig name subnetid vnet subnets id applicationgatewaybackendaddresspoolsid backendpool id vmssconfig new azvmssconfig location japaneast skucapacity skuname standard upgradepolicymode automatic zone vmimage get azimage resourcegroupname rgname imagename vmimagename set azvmssstorageprofile vmssconfig imagereferenceid vmimage id osdiskcreateoption fromimage set azvmssosprofile vmssconfig adminusername vmssadminusername adminpassword vmssadminpassword computernameprefix scalesetname add azvmssnetworkinterfaceconfiguration virtualmachinescaleset vmssconfig name netconfig primary true ipconfiguration ipconfig new azvmss resourcegroupname rgname name scalesetname virtualmachinescaleset vmssconfig debug environment data ps c users koyasuda psversiontable name value psversion psedition desktop pscompatibleversions buildversion clrversion wsmanstackversion psremotingprotocolversion serializationversion module versions moduletype version name exportedcommands manifest appbackgroundtask disable appbackgroundtaskdiagnosticlog enable appbackgroundtaskdiagnosticlog set appbackgroundtaskresourcepolicy unregister ap manifest applocker get applockerfileinformation get applockerpolicy new applockerpolicy set applockerpolicy manifest appvclient add appvclientconnectiongroup add appvclientpackage add appvpublishingserver disable appv manifest appx add appxpackage get appxpackage get appxpackagemanifest remove appxpackage script assignedaccess clear assignedaccess get assignedaccess set assignedaccess manifest bitlocker unlock bitlocker suspend bitlocker resume bitlocker remove bitlockerkeyprotector manifest bitstransfer add bitsfile complete bitstransfer get bitstransfer remove bitstransfer manifest branchcache add bcdatacacheextension clear bccache disable bc disable bcdowngrading manifest cimcmdlets get cimassociatedinstance get cimclass get ciminstance get cimsession manifest configci get systemdriver new cipolicyrule new cipolicy get cipolicy manifest configdefender get mppreference set mppreference add mppreference remove mppreference manifest defender get mppreference set mppreference add mppreference remove mppreference manifest deliveryoptimization delete deliveryoptimizationcache get deliveryoptimizationstatus set deliveryoptimizationstatus get deliveryoptimizationperfsna manifest directaccessclientcomponents disable damanualentrypointselection enable damanualentrypointselection get daclientexperienceconfiguration get daentrypointtab script dism add appxprovisionedpackage add windowsdriver add windowscapability add windowsimage manifest dnsclient resolve dnsname clear dnsclientcache get dnsclient get dnsclientcache manifest eventtracingmanagement start etwtracesession new etwtracesession get etwtracesession update etwtracesession manifest hgsclient get hgsattestationbaselinepolicy get hgsclientconfiguration test hgsclientconfiguration set hgsclientconfiguration manifest hgsdiagnostics new hgstracetarget get hgstrace get hgstracefiledata test hgstracetarget manifest hostnetworkingservice remove hnsnamespace remove hnsendpoint get hnsendpoint get hnsnamespace binary hyper v add vmassignabledevice add vmdvddrive add vmfibrechannelhba add vmgpupartitionadapter binary hyper v add vmdvddrive add vmfibrechannelhba add vmharddiskdrive add vmmigrationnetwork manifest international get windefaultinputmethodoverride set windefaultinputmethodoverride get winhomelocation set winhomelocation manifest iscsi get iscsitargetportal new iscsitargetportal remove iscsitargetportal update iscsitargetportal script ise new isesnippet import isesnippet get isesnippet manifest kds add kdsrootkey get kdsrootkey test kdsrootkey set kdsconfiguration manifest microsoft powershell archive compress archive expand archive manifest microsoft powershell diagnostics get winevent get counter import counter export counter manifest microsoft powershell host start transcript stop transcript manifest microsoft powershell localaccounts add localgroupmember disable localuser enable localuser get localgroup manifest microsoft powershell management add content clear content clear itemproperty join path script microsoft powershell odatautils export odataendpointproxy manifest microsoft powershell security get acl set acl get pfxcertificate get credential manifest microsoft powershell utility format list format custom format table format wide manifest microsoft wsman management disable wsmancredssp enable wsmancredssp get wsmancredssp set wsmanquickconfig manifest mmagent disable mmagent enable mmagent set mmagent get mmagent manifest msdtc new dtcdiagnostictransaction complete dtcdiagnostictransaction join dtcdiagnosticresourcemanager receive dtcdiagnostictransact manifest netadapter disable netadapter disable netadapterbinding disable netadapterchecksumoffload disable netadapterencapsulatedpackettaskoffload manifest netconnection get netconnectionprofile set netconnectionprofile manifest netdiagnostics get netview manifest neteventpacketcapture new neteventsession remove neteventsession get neteventsession set neteventsession manifest netlbfo add netlbfoteammember add netlbfoteamnic get netlbfoteam get netlbfoteammember manifest netnat get netnat get netnatexternaladdress get netnatstaticmapping get netnatsession manifest netqos get netqospolicy set netqospolicy remove netqospolicy new netqospolicy manifest netsecurity get dapolicychange new netipsecauthproposal new netipsecmainmodecryptoproposal new netipsecquickmodecryptoproposal manifest netswitchteam new netswitchteam remove netswitchteam get netswitchteam rename netswitchteam manifest nettcpip get netipaddress get netipinterface get get manifest networkconnectivitystatus get daconnectionstatus get ncsipolicyconfiguration reset ncsipolicyconfiguration set ncsipolicyconfiguration manifest networkswitchmanager disable networkswitchethernetport enable networkswitchethernetport get networkswitchethernetport remove networkswitchethernetp manifest networktransition add netiphttpscertbinding disable netdnstransitionconfiguration disable netiphttpsprofile disable netnattransitionconfiguratio manifest pcsvdevice get pcsvdevice start pcsvdevice stop pcsvdevice restart pcsvdevice binary persistentmemory get pmemdisk get pmemphysicaldevice get pmemunusedregion new pmemdisk manifest pki add certificateenrollmentpolicyserver export certificate export pfxcertificate get certificateautoenrollmentpolicy manifest pnpdevice get pnpdevice get pnpdeviceproperty enable pnpdevice disable pnpdevice manifest printmanagement add printer add printerdriver add printerport get printconfiguration binary processmitigations get processmitigation set processmitigation convertto processmitigationpolicy script provisioning install provisioningpackage export provisioningpackage install trustedprovisioningcertificate export trace manifest psdesiredstateconfiguration set dsclocalconfigurationmanager start dscconfiguration test dscconfiguration publish dscconfiguration script psdiagnostics disable pstrace disable pswsmancombinedtrace disable wsmantrace enable pstrace binary psscheduledjob new jobtrigger add jobtrigger remove jobtrigger get jobtrigger manifest psworkflow new psworkflowexecutionoption new psworkflowsession nwsn manifest psworkflowutility invoke asworkflow manifest scheduledtasks get scheduledtask set scheduledtask register scheduledtask unregister scheduledtask manifest secureboot confirm securebootuefi set securebootuefi get securebootuefi format securebootuefi manifest smbshare get smbshare remove smbshare set smbshare block smbshareaccess manifest smbwitness get smbwitnessclient move smbwitnessclient gsmbw msmbw manifest startlayout export startlayout import startlayout export startlayoutedgeassets get startapps manifest storage add initiatoridtomaskingset add partitionaccesspath add physicaldisk add storagefaultdomain manifest storagebuscache clear storagebusdisk disable storagebuscache disable storagebusdisk enable storagebuscache manifest tls new tlssessionticketkey enable tlssessionticketkey disable tlssessionticketkey export tlssessionticketkey manifest troubleshootingpack get troubleshootingpack invoke troubleshootingpack manifest trustedplatformmodule get tpm initialize tpm clear tpm unblock tpm binary uev clear uevconfiguration clear uevappxpackage restore uevbackup set uevtemplateprofile manifest vpnclient add vpnconnection set vpnconnection remove vpnconnection get vpnconnection manifest wdac get odbcdriver set odbcdriver get odbcdsn add odbcdsn manifest whea get wheamemorypolicy set wheamemorypolicy manifest windowsdeveloperlicense get windowsdeveloperlicense unregister windowsdeveloperlicense show windowsdeveloperlicenseregistration script windowserrorreporting enable windowserrorreporting disable windowserrorreporting get windowserrorreporting manifest windowssearch get windowssearchsetting set windowssearchsetting manifest windowsupdate get windowsupdatelog manifest windowsupdateprovider get wuaversion get wulastinstallationdate get wulastscansuccessdate get wuispendingreboot ディレクトリ c program files microsoft azure information protection powershell moduletype version name exportedcommands binary azureinformationprotection clear rmsauthentication get rmsfilestatus get rmsserver get rmsserverauthentication ディレクトリ c program files microsoft message analyzer powershell moduletype version name exportedcommands script pef debug output ps c users koyasuda new azvmss resourcegroupname rgname name scalesetname virtualmachinescaleset vmssconfig debug デバッグ newazurermvmss begin processing with parameterset defaultparameter デバッグ using account id koyasuda microsoft com デバッグ authenticating using account koyasuda microsoft com environment azurecloud tenant デバッグ authenticating using configuration values domain endpoint clientid clientredirect urn ietf wg oauth oob resourceclienturi validateauthority true デバッグ acquiring token using context with authority correlationid validateauthority true デバッグ acquiring token using adalconfiguration with domain adendpoint clientid clientredirecturi urn ietf wg oauth oob デバッグ information loggerbase cs adal pcl desktop with assembly version file version and informational version is running デバッグ information loggerbase cs adal pcl desktop with assembly version file version and informational version is running デバッグ information loggerbase cs token acquisition started cachetype null authentication target user authority host login microsoftonline com デバッグ information loggerbase cs token acquisition started authority resource clientid cachetype null authentication target user デバッグ verbose loggerbase cs loading from cache デバッグ verbose loggerbase cs loading from cache デバッグ information loggerbase cs deserialized items to token cache デバッグ verbose loggerbase cs looking up cache for a token デバッグ verbose loggerbase cs looking up cache for a token デバッグ information loggerbase cs an item matching the requested resource was found in the cache デバッグ information loggerbase cs an item matching the requested resource was found in the cache デバッグ information loggerbase cs minutes left until token in cache expires デバッグ information loggerbase cs minutes left until token in cache expires デバッグ information loggerbase cs a matching item access token or refresh token or both was found in the cache デバッグ information loggerbase cs a matching item access token or refresh token or both was found in the cache デバッグ information loggerbase cs token acquisition finished successfully an access token was returned expira tion time デバッグ information loggerbase cs token acquisition finished successfully an access token was returned expira tion time token hash k user id デバッグ renewing token with type bearer expiry multipleresource true tenant userid koya suda microsoft com デバッグ user info for token displayid koyasuda microsoft com name koya yasuda idprovider uid デバッグ checking token expiration token expires comparing to with threshold calculated time until token expiry デバッグ http request http method put absolute uri headers x ms client request id accept language en us body sku name standard capacity properties upgradepolicy mode automatic automaticosupgradepolicy enableautomaticosupgrade false automaticrepairspolicy enabled false virtualmachineprofile osprofile computernameprefix testuser adminusername testuser adminpassword storageprofile imagereference id subscriptions resourcegroups providers microsoft compute images image image osdisk writeacceleratorenabled false createoption fromimage networkprofile networkinterfaceconfigurations name netconfig properties primary true enableacceleratednetworking false enableipforwarding false zones location japaneast tags デバッグ http response status code badrequest headers pragma no cache x ms ratelimit remaining resource microsoft compute microsoft compute strict transport security max age includesubdomains x ms request id cache control no cache server microsoft httpapi microsoft httpapi x ms ratelimit remaining subscription writes x ms correlation request id x ms routing request id eastasia x content type options nosniff date fri mar gmt body error code badrequest message automatic repairs feature on virtual machine scale set is supported when singleplacementgroup is enabled デバッグ azureqosevent commandname new azvmss issuccess true duration デバッグ finish sending metric デバッグ newazurermvmss end processing new azvmss automatic repairs feature on virtual machine scale set is supported when singleplacementgroup is enabled errorcode badrequest errormessage automatic repairs feature on virtual machine scale set is supported when singleplacementgroup is enabled errortarget statuscode reasonphrase bad request operationid 発生場所 行 文字 new azvmss resourcegroupname rgname name scalesetname virtualmac categoryinfo closeerror 、computecloudexception fullyqualifiederrorid microsoft azure commands compute automation newazurermvmss デバッグ azureqosevent commandname new azvmss issuccess false duration exception microsoft azure commands compute common computecloudexception automatic repairs fea ture on virtual machine scale set is supported when singleplacementgroup is enabled errorcode badrequest errormessage automatic repairs feature on virtual machine scale set is supported when singleplacementgroup is enabled errortarget statuscode reasonphrase bad request operationid microsoft rest azure cloudexception automatic repairs feature on virtual machine scale set is supported when singleplacementgroup is en abled 場所 microsoft azure management compute virtualmachinescalesetsoperations d movenext 直前に例外がスローされた場所からのスタック トレースの終わり 場所 system runtime exceptionservices exceptiondispatchinfo throw 場所 system runtime compilerservices taskawaiter handlenonsuccessanddebuggernotification task task 場所 system runtime compilerservices configuredtaskawaitable configuredtaskawaiter getresult 場所 microsoft azure management compute virtualmachinescalesetsoperations d movenext 直前に例外がスローされた場所からのスタック トレースの終わり 場所 system runtime exceptionservices exceptiondispatchinfo throw 場所 system runtime compilerservices taskawaiter handlenonsuccessanddebuggernotification task task 場所 system runtime compilerservices configuredtaskawaitable configuredtaskawaiter getresult 場所 microsoft azure management compute virtualmachinescalesetsoperationsextensions d movenext 直前に例外がスローされた場所からのスタック トレースの終わり 場所 system runtime exceptionservices exceptiondispatchinfo throw 場所 system runtime compilerservices taskawaiter handlenonsuccessanddebuggernotification task task 場所 system runtime compilerservices taskawaiter getresult 場所 microsoft azure management compute virtualmachinescalesetsoperationsextensions createorupdate ivirtualmachinescalesetsoperations operations string resourcegroupname string vmscalesetna me virtualmachinescaleset parameters 場所 microsoft azure commands compute automation newazurermvmss b 場所 microsoft azure commands compute computeclientbasecmdlet executeclientaction action action 内部例外スタック トレースの終わり 場所 microsoft azure commands compute computeclientbasecmdlet executeclientaction action action 場所 microsoft windowsazure commands utilities common azurepscmdlet processrecord デバッグ finish sending metric デバッグ newazurermvmss end processing ps c users koyasuda error output ps c users koyasuda resolve azerror 警告 breaking changes in the cmdlet resolve azerror 警告 the resolve error alias will be removed in a future release please change any scripts that use this alias to use resolve azerror instead 警告 note go to for steps to suppress this breaking change warning and other information on breaking changes in azure powershell historyid requestid message automatic repairs feature on virtual machine scale set is supported when singleplacementgroup is enabled errorcode badrequest errormessage automatic repairs feature on virtual machine scale set is supported when singleplacementgroup is enabled errortarget statuscode reasonphrase bad request operationid servermessage serverresponse requestmessage invocationinfo new azvmss line new azvmss resourcegroupname rgname name scalesetname virtualmachinescaleset vmssconfig debug position 発生場所 行 文字 new azvmss resourcegroupname rgname name scalesetname virtualmac stacktrace 場所 microsoft azure commands compute computeclientbasecmdlet executeclientaction action action 場所 microsoft windowsazure commands utilities common azurepscmdlet processrecord historyid historyid requestid message automatic repairs feature on virtual machine scale set is supported when singleplacementgroup is enabled errorcode badrequest errormessage automatic repairs feature on virtual machine scale set is supported when singleplacementgroup is enabled errortarget statuscode reasonphrase bad request operationid servermessage serverresponse requestmessage invocationinfo new azvmss line new azvmss position 発生場所 行 文字 new azvmss stacktrace 場所 microsoft azure commands compute computeclientbasecmdlet executeclientaction action action 場所 microsoft windowsazure commands utilities common azurepscmdlet processrecord historyid | 0 |
14,837 | 2,831,389,923 | IssuesEvent | 2015-05-24 15:54:47 | nobodyguy/dslrdashboard | https://api.github.com/repos/nobodyguy/dslrdashboard | closed | LRTimelapse: Display JPG for next capture sometimes not working | auto-migrated Priority-Medium Type-Defect | ```
What steps will reproduce the problem?
1. Enable the checkbox "Display JPG for next capture"
2. Wait for next capture and preview
What is the expected output? What do you see instead?
Sometimes the checkbox remains checked and no new JPG is loaded. I checked the
camera settings using the camera menu (Q-button of my Canon) and saw that the
camera was in RAW only mode. After closing the LRTimelapse screen I saw that
DslrDashboard showed that RAW+JPG was enabled. After switching from RAW+JPG to
RAW and back to RAW+JPG using DslrDashboard main screen the setting in the
camera menu was changed and the option "Display JPG for next capture" in the
LRTimelapse screen worked again.
This also happend while testing the new auto holy-grail option.
What version of the product are you using? On what operating system?
DslrDashboard v0.30.30_1 on Android v4.3, Canon EOS 60D v1.1.1, TP-Link
TL-MR3040 V2 with ddserver v0.2-4.
```
Original issue reported on code.google.com by `christ...@milindur.de` on 10 Sep 2013 at 2:48 | 1.0 | LRTimelapse: Display JPG for next capture sometimes not working - ```
What steps will reproduce the problem?
1. Enable the checkbox "Display JPG for next capture"
2. Wait for next capture and preview
What is the expected output? What do you see instead?
Sometimes the checkbox remains checked and no new JPG is loaded. I checked the
camera settings using the camera menu (Q-button of my Canon) and saw that the
camera was in RAW only mode. After closing the LRTimelapse screen I saw that
DslrDashboard showed that RAW+JPG was enabled. After switching from RAW+JPG to
RAW and back to RAW+JPG using DslrDashboard main screen the setting in the
camera menu was changed and the option "Display JPG for next capture" in the
LRTimelapse screen worked again.
This also happend while testing the new auto holy-grail option.
What version of the product are you using? On what operating system?
DslrDashboard v0.30.30_1 on Android v4.3, Canon EOS 60D v1.1.1, TP-Link
TL-MR3040 V2 with ddserver v0.2-4.
```
Original issue reported on code.google.com by `christ...@milindur.de` on 10 Sep 2013 at 2:48 | defect | lrtimelapse display jpg for next capture sometimes not working what steps will reproduce the problem enable the checkbox display jpg for next capture wait for next capture and preview what is the expected output what do you see instead sometimes the checkbox remains checked and no new jpg is loaded i checked the camera settings using the camera menu q button of my canon and saw that the camera was in raw only mode after closing the lrtimelapse screen i saw that dslrdashboard showed that raw jpg was enabled after switching from raw jpg to raw and back to raw jpg using dslrdashboard main screen the setting in the camera menu was changed and the option display jpg for next capture in the lrtimelapse screen worked again this also happend while testing the new auto holy grail option what version of the product are you using on what operating system dslrdashboard on android canon eos tp link tl with ddserver original issue reported on code google com by christ milindur de on sep at | 1 |
238,860 | 7,783,689,626 | IssuesEvent | 2018-06-06 10:49:53 | strapi/strapi | https://api.github.com/repos/strapi/strapi | closed | Content type won't save | priority: medium status: can't reproduce 🙃 type: bug 🐛 | <!-- ⚠️ If you do not respect this template your issue will be closed. -->
<!-- ⚠️ Before writing your issue make sure you are using:-->
<!-- Node 9.x.x -->
<!-- npm 5.x.x -->
<!-- The latest version of Strapi. -->
**Informations**
- **Node.js version**: v8.11.2
- **npm version**: 5.6.0
- **Strapi version**: 3.0.0-alpha.12.2
- **Database**: Mongodb 3.6.5
- **Operating system**: ubuntu 16.04
**What is the current behavior?**
Content type wont save unless I restart my strapi node server.
(same issue here https://github.com/strapi/strapi/issues/487 but it was closed ??)
**Steps to reproduce the problem**
Try to create content type add some fields and press "save".
**What is the expected behavior?**
Created content type with fields.
**Suggested solutions**
Have no suggestions... maybe somehow automatically restart server or at least inform user with "restart your server" instead of "error occured".
<!-- ⚠️ Make sure to browse the opened and closed issues before submit your issue. -->
| 1.0 | Content type won't save - <!-- ⚠️ If you do not respect this template your issue will be closed. -->
<!-- ⚠️ Before writing your issue make sure you are using:-->
<!-- Node 9.x.x -->
<!-- npm 5.x.x -->
<!-- The latest version of Strapi. -->
**Informations**
- **Node.js version**: v8.11.2
- **npm version**: 5.6.0
- **Strapi version**: 3.0.0-alpha.12.2
- **Database**: Mongodb 3.6.5
- **Operating system**: ubuntu 16.04
**What is the current behavior?**
Content type wont save unless I restart my strapi node server.
(same issue here https://github.com/strapi/strapi/issues/487 but it was closed ??)
**Steps to reproduce the problem**
Try to create content type add some fields and press "save".
**What is the expected behavior?**
Created content type with fields.
**Suggested solutions**
Have no suggestions... maybe somehow automatically restart server or at least inform user with "restart your server" instead of "error occured".
<!-- ⚠️ Make sure to browse the opened and closed issues before submit your issue. -->
| non_defect | content type won t save informations node js version npm version strapi version alpha database mongodb operating system ubuntu what is the current behavior content type wont save unless i restart my strapi node server same issue here but it was closed steps to reproduce the problem try to create content type add some fields and press save what is the expected behavior created content type with fields suggested solutions have no suggestions maybe somehow automatically restart server or at least inform user with restart your server instead of error occured | 0 |
71,226 | 23,493,656,684 | IssuesEvent | 2022-08-17 21:32:47 | department-of-veterans-affairs/vets-design-system-documentation | https://api.github.com/repos/department-of-veterans-affairs/vets-design-system-documentation | closed | Add a Yarn command to transpile JavaScript for IE11 testing (web-components branch only) | 508-defect-4 accessibility testing | Original Issue: https://github.com/department-of-veterans-affairs/vets-design-system-documentation/issues/401
Referencing the above original issue, we were able to implement a solution that worked to solve the errors that were occurring in `master` branch. At the time of that issue being resolved, Storybook was fully functional in IE11 for the master branch. We were unable, however, to solve the issue of getting it to load the same way in the `web-components` branch. As that ticket was half resolved, we're creating a new issue here to clearly lay out the half of the task that remains to be done, to avoid it being overlooked due to half of the other one being solved.
At present, the `web-components` branch still gives errors in IE11. The error information we're receiving seems to be along the lines of `NotSupportedError` without a lot of other information. Even with babel settings enabled for the build it seems to still struggle. The desired end result is that Storybook would be usable in the same manner in IE11 on the `web-components` branch as it currently works on `master`. | 1.0 | Add a Yarn command to transpile JavaScript for IE11 testing (web-components branch only) - Original Issue: https://github.com/department-of-veterans-affairs/vets-design-system-documentation/issues/401
Referencing the above original issue, we were able to implement a solution that worked to solve the errors that were occurring in `master` branch. At the time of that issue being resolved, Storybook was fully functional in IE11 for the master branch. We were unable, however, to solve the issue of getting it to load the same way in the `web-components` branch. As that ticket was half resolved, we're creating a new issue here to clearly lay out the half of the task that remains to be done, to avoid it being overlooked due to half of the other one being solved.
At present, the `web-components` branch still gives errors in IE11. The error information we're receiving seems to be along the lines of `NotSupportedError` without a lot of other information. Even with babel settings enabled for the build it seems to still struggle. The desired end result is that Storybook would be usable in the same manner in IE11 on the `web-components` branch as it currently works on `master`. | defect | add a yarn command to transpile javascript for testing web components branch only original issue referencing the above original issue we were able to implement a solution that worked to solve the errors that were occurring in master branch at the time of that issue being resolved storybook was fully functional in for the master branch we were unable however to solve the issue of getting it to load the same way in the web components branch as that ticket was half resolved we re creating a new issue here to clearly lay out the half of the task that remains to be done to avoid it being overlooked due to half of the other one being solved at present the web components branch still gives errors in the error information we re receiving seems to be along the lines of notsupportederror without a lot of other information even with babel settings enabled for the build it seems to still struggle the desired end result is that storybook would be usable in the same manner in on the web components branch as it currently works on master | 1 |
96,246 | 10,927,300,203 | IssuesEvent | 2019-11-22 16:24:06 | DiscipleTools/disciple-tools-theme | https://api.github.com/repos/DiscipleTools/disciple-tools-theme | closed | Contacts: Help icons to open modals | documentation | Add an icon next to the Quick Action drop down that opens the help modal explaining how to use the quick actions.
<img width="506" alt="quick actions help" src="https://user-images.githubusercontent.com/43966676/67526609-bdaa2c00-f67a-11e9-8923-c06704392037.png">
| 1.0 | Contacts: Help icons to open modals - Add an icon next to the Quick Action drop down that opens the help modal explaining how to use the quick actions.
<img width="506" alt="quick actions help" src="https://user-images.githubusercontent.com/43966676/67526609-bdaa2c00-f67a-11e9-8923-c06704392037.png">
| non_defect | contacts help icons to open modals add an icon next to the quick action drop down that opens the help modal explaining how to use the quick actions img width alt quick actions help src | 0 |
392,175 | 26,928,142,151 | IssuesEvent | 2023-02-07 15:06:04 | WordPress/Documentation-Issue-Tracker | https://api.github.com/repos/WordPress/Documentation-Issue-Tracker | closed | [HelpHub] Update PHP page | user documentation re-categorization project | <!--
Please fill out the following sections with as many details as you can.
We can't work on fixing an issue unless we have all the details.
So please be sure your submission is complete; if it's not, it will be marked as incomplete, and closed without being fixed.
-->
## Issue Description
<!-- Please write a brief description of the issue. -->
Another article written as a page instead of an article. This is very simple information that any user must learn.
## URL of the Page with the Issue
<!--
Please provide a link to the documentation where the issue is.-->
https://wordpress.org/documentation/update-php/
## Suggested Fix
<!--
If possible, please suggest how we can correct this issue.
-->
Keep in HH and add as an article under /documentation/technicalguides/maintenance | 1.0 | [HelpHub] Update PHP page - <!--
Please fill out the following sections with as many details as you can.
We can't work on fixing an issue unless we have all the details.
So please be sure your submission is complete; if it's not, it will be marked as incomplete, and closed without being fixed.
-->
## Issue Description
<!-- Please write a brief description of the issue. -->
Another article written as a page instead of an article. This is very simple information that any user must learn.
## URL of the Page with the Issue
<!--
Please provide a link to the documentation where the issue is.-->
https://wordpress.org/documentation/update-php/
## Suggested Fix
<!--
If possible, please suggest how we can correct this issue.
-->
Keep in HH and add as an article under /documentation/technicalguides/maintenance | non_defect | update php page please fill out the following sections with as many details as you can we can t work on fixing an issue unless we have all the details so please be sure your submission is complete if it s not it will be marked as incomplete and closed without being fixed issue description another article written as a page instead of an article this is very simple information that any user must learn url of the page with the issue please provide a link to the documentation where the issue is suggested fix if possible please suggest how we can correct this issue keep in hh and add as an article under documentation technicalguides maintenance | 0 |
456,335 | 13,149,605,718 | IssuesEvent | 2020-08-09 06:22:27 | wso2/product-apim | https://api.github.com/repos/wso2/product-apim | opened | Error while creating an application when giving some long description | Priority/Normal Type/Bug | ### Description:
Unable to create an application with a long description. In the UI level it is not limiting / restricting the length.
### Steps to reproduce:
Try to create an Application with long description.
### Affected Product Version:
APIM 3.2.0-RC2
### Environment details (with versions):
- OS: Mac OS
{code:xml}
TID: [-1234] [api/am/store] [2020-08-08 21:57:01,886] ERROR {org.wso2.carbon.apimgt.impl.dao.ApiMgtDAO} - Failed to add Application org.h2.jdbc.JdbcSQLDataException: Value too long for column """DESCRIPTION"" VARCHAR(512)": "'my abic test application 1234556767678 my abic test application 123455my abic test application 1234556767678 my abic test appli... (1820)"; SQL statement:
INSERT INTO AM_APPLICATION (NAME, SUBSCRIBER_ID, APPLICATION_TIER, CALLBACK_URL, DESCRIPTION, APPLICATION_STATUS, GROUP_ID, CREATED_BY, CREATED_TIME, UPDATED_TIME, UUID, TOKEN_TYPE) VALUES (?,?,?,?,?,?,?,?,?,?,?,?) [22001-199]
at org.h2.message.DbException.getJdbcSQLException(DbException.java:455)
at org.h2.message.DbException.getJdbcSQLException(DbException.java:427)
at org.h2.message.DbException.get(DbException.java:205)
at org.h2.table.Column.validateConvertUpdateSequence(Column.java:441)
at org.h2.table.Table.validateConvertUpdateSequence(Table.java:824)
at org.h2.command.dml.Insert.insertRows(Insert.java:175)
at org.h2.command.dml.Insert.update(Insert.java:132)
at org.h2.command.CommandContainer.update(CommandContainer.java:133)
at org.h2.command.Command.executeUpdate(Command.java:267)
at org.h2.jdbc.JdbcPreparedStatement.executeUpdateInternal(JdbcPreparedStatement.java:200)
at org.h2.jdbc.JdbcPreparedStatement.executeUpdate(JdbcPreparedStatement.java:154)
at sun.reflect.GeneratedMethodAccessor62.invoke(Unknown Source)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.apache.tomcat.jdbc.pool.StatementFacade$StatementProxy.invoke(StatementFacade.java:114)
at com.sun.proxy.$Proxy49.executeUpdate(Unknown Source)
at org.wso2.carbon.apimgt.impl.dao.ApiMgtDAO.addApplication_aroundBody186(ApiMgtDAO.java:4053)
at org.wso2.carbon.apimgt.impl.dao.ApiMgtDAO.addApplication(ApiMgtDAO.java:4002)
at org.wso2.carbon.apimgt.impl.dao.ApiMgtDAO.addApplication_aroundBody156(ApiMgtDAO.java:3398)
at org.wso2.carbon.apimgt.impl.dao.ApiMgtDAO.addApplication(ApiMgtDAO.java:3391)
at org.wso2.carbon.apimgt.impl.APIConsumerImpl.addApplication_aroundBody138(APIConsumerImpl.java:3620)
at org.wso2.carbon.apimgt.impl.APIConsumerImpl.addApplication(APIConsumerImpl.java:3528)
at org.wso2.carbon.apimgt.impl.UserAwareAPIConsumer.addApplication_aroundBody8(UserAwareAPIConsumer.java:86)
at org.wso2.carbon.apimgt.impl.UserAwareAPIConsumer.addApplication(UserAwareAPIConsumer.java:84)
at org.wso2.carbon.apimgt.rest.api.store.v1.impl.ApplicationsApiServiceImpl.applicationsPost(ApplicationsApiServiceImpl.java:182)
at org.wso2.carbon.apimgt.rest.api.store.v1.ApplicationsApi.applicationsPost(ApplicationsApi.java:451)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.apache.cxf.service.invoker.AbstractInvoker.performInvocation(AbstractInvoker.java:179)
at org.apache.cxf.service.invoker.AbstractInvoker.invoke(AbstractInvoker.java:96)
at org.apache.cxf.jaxrs.JAXRSInvoker.invoke(JAXRSInvoker.java:193)
at org.apache.cxf.jaxrs.JAXRSInvoker.invoke(JAXRSInvoker.java:103)
at org.apache.cxf.interceptor.ServiceInvokerInterceptor$1.run(ServiceInvokerInterceptor.java:59)
at org.apache.cxf.interceptor.ServiceInvokerInterceptor.handleMessage(ServiceInvokerInterceptor.java:96)
at org.apache.cxf.phase.PhaseInterceptorChain.doIntercept(PhaseInterceptorChain.java:308)
at org.apache.cxf.transport.ChainInitiationObserver.onMessage(ChainInitiationObserver.java:121)
at org.apache.cxf.transport.http.AbstractHTTPDestination.invoke(AbstractHTTPDestination.java:267)
at org.apache.cxf.transport.servlet.ServletController.invokeDestination(ServletController.java:234)
at org.apache.cxf.transport.servlet.ServletController.invoke(ServletController.java:208)
at org.apache.cxf.transport.servlet.ServletController.invoke(ServletController.java:160)
at org.apache.cxf.transport.servlet.CXFNonSpringServlet.invoke(CXFNonSpringServlet.java:216)
at org.apache.cxf.transport.servlet.AbstractHTTPServlet.handleRequest(AbstractHTTPServlet.java:301)
at org.apache.cxf.transport.servlet.AbstractHTTPServlet.doPost(AbstractHTTPServlet.java:220)
at javax.servlet.http.HttpServlet.service(HttpServlet.java:660)
at org.apache.cxf.transport.servlet.AbstractHTTPServlet.service(AbstractHTTPServlet.java:276)
at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:231)
at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:166)
at org.apache.tomcat.websocket.server.WsFilter.doFilter(WsFilter.java:53)
at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:193)
at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:166)
at org.apache.catalina.core.StandardWrapperValve.invoke(StandardWrapperValve.java:202)
at org.apache.catalina.core.StandardContextValve.invoke(StandardContextValve.java:96)
at org.apache.catalina.authenticator.AuthenticatorBase.invoke(AuthenticatorBase.java:541)
at org.apache.catalina.core.StandardHostValve.invoke(StandardHostValve.java:139)
at org.apache.catalina.valves.ErrorReportValve.invoke(ErrorReportValve.java:92)
at org.wso2.carbon.identity.context.rewrite.valve.TenantContextRewriteValve.invoke(TenantContextRewriteValve.java:86)
at org.wso2.carbon.identity.authz.valve.AuthorizationValve.invoke(AuthorizationValve.java:110)
at org.wso2.carbon.identity.auth.valve.AuthenticationValve.invoke(AuthenticationValve.java:75)
at org.wso2.carbon.tomcat.ext.valves.CompositeValve.continueInvocation(CompositeValve.java:99)
at org.wso2.carbon.tomcat.ext.valves.TomcatValveContainer.invokeValves(TomcatValveContainer.java:49)
at org.wso2.carbon.tomcat.ext.valves.CompositeValve.invoke(CompositeValve.java:62)
at org.wso2.carbon.tomcat.ext.valves.CarbonStuckThreadDetectionValve.invoke(CarbonStuckThreadDetectionValve.java:145)
at org.apache.catalina.valves.AbstractAccessLogValve.invoke(AbstractAccessLogValve.java:688)
at org.wso2.carbon.tomcat.ext.valves.CarbonContextCreatorValve.invoke(CarbonContextCreatorValve.java:57)
at org.wso2.carbon.tomcat.ext.valves.RequestCorrelationIdValve.invoke(RequestCorrelationIdValve.java:119)
at org.apache.catalina.core.StandardEngineValve.invoke(StandardEngineValve.java:74)
at org.apache.catalina.connector.CoyoteAdapter.service(CoyoteAdapter.java:343)
at org.apache.coyote.http11.Http11Processor.service(Http11Processor.java:367)
at org.apache.coyote.AbstractProcessorLight.process(AbstractProcessorLight.java:65)
at org.apache.coyote.AbstractProtocol$ConnectionHandler.process(AbstractProtocol.java:868)
at org.apache.tomcat.util.net.NioEndpoint$SocketProcessor.doRun(NioEndpoint.java:1639)
at org.apache.tomcat.util.net.SocketProcessorBase.run(SocketProcessorBase.java:49)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
at org.apache.tomcat.util.threads.TaskThread$WrappingRunnable.run(TaskThread.java:61)
at java.lang.Thread.run(Thread.java:748)
TID: [-1234] [api/am/store] [2020-08-08 21:57:02,063] ERROR {org.wso2.carbon.apimgt.rest.api.store.v1.impl.ApplicationsApiServiceImpl} - Error while adding a new application for the user admin org.wso2.carbon.apimgt.api.APIManagementException: Failed to add Application
at org.wso2.carbon.apimgt.impl.dao.ApiMgtDAO.handleException_aroundBody320(ApiMgtDAO.java:7297)
at org.wso2.carbon.apimgt.impl.dao.ApiMgtDAO.handleException(ApiMgtDAO.java:7295)
at org.wso2.carbon.apimgt.impl.dao.ApiMgtDAO.addApplication_aroundBody186(ApiMgtDAO.java:4065)
{code} | 1.0 | Error while creating an application when giving some long description - ### Description:
Unable to create an application with a long description. In the UI level it is not limiting / restricting the length.
### Steps to reproduce:
Try to create an Application with long description.
### Affected Product Version:
APIM 3.2.0-RC2
### Environment details (with versions):
- OS: Mac OS
{code:xml}
TID: [-1234] [api/am/store] [2020-08-08 21:57:01,886] ERROR {org.wso2.carbon.apimgt.impl.dao.ApiMgtDAO} - Failed to add Application org.h2.jdbc.JdbcSQLDataException: Value too long for column """DESCRIPTION"" VARCHAR(512)": "'my abic test application 1234556767678 my abic test application 123455my abic test application 1234556767678 my abic test appli... (1820)"; SQL statement:
INSERT INTO AM_APPLICATION (NAME, SUBSCRIBER_ID, APPLICATION_TIER, CALLBACK_URL, DESCRIPTION, APPLICATION_STATUS, GROUP_ID, CREATED_BY, CREATED_TIME, UPDATED_TIME, UUID, TOKEN_TYPE) VALUES (?,?,?,?,?,?,?,?,?,?,?,?) [22001-199]
at org.h2.message.DbException.getJdbcSQLException(DbException.java:455)
at org.h2.message.DbException.getJdbcSQLException(DbException.java:427)
at org.h2.message.DbException.get(DbException.java:205)
at org.h2.table.Column.validateConvertUpdateSequence(Column.java:441)
at org.h2.table.Table.validateConvertUpdateSequence(Table.java:824)
at org.h2.command.dml.Insert.insertRows(Insert.java:175)
at org.h2.command.dml.Insert.update(Insert.java:132)
at org.h2.command.CommandContainer.update(CommandContainer.java:133)
at org.h2.command.Command.executeUpdate(Command.java:267)
at org.h2.jdbc.JdbcPreparedStatement.executeUpdateInternal(JdbcPreparedStatement.java:200)
at org.h2.jdbc.JdbcPreparedStatement.executeUpdate(JdbcPreparedStatement.java:154)
at sun.reflect.GeneratedMethodAccessor62.invoke(Unknown Source)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.apache.tomcat.jdbc.pool.StatementFacade$StatementProxy.invoke(StatementFacade.java:114)
at com.sun.proxy.$Proxy49.executeUpdate(Unknown Source)
at org.wso2.carbon.apimgt.impl.dao.ApiMgtDAO.addApplication_aroundBody186(ApiMgtDAO.java:4053)
at org.wso2.carbon.apimgt.impl.dao.ApiMgtDAO.addApplication(ApiMgtDAO.java:4002)
at org.wso2.carbon.apimgt.impl.dao.ApiMgtDAO.addApplication_aroundBody156(ApiMgtDAO.java:3398)
at org.wso2.carbon.apimgt.impl.dao.ApiMgtDAO.addApplication(ApiMgtDAO.java:3391)
at org.wso2.carbon.apimgt.impl.APIConsumerImpl.addApplication_aroundBody138(APIConsumerImpl.java:3620)
at org.wso2.carbon.apimgt.impl.APIConsumerImpl.addApplication(APIConsumerImpl.java:3528)
at org.wso2.carbon.apimgt.impl.UserAwareAPIConsumer.addApplication_aroundBody8(UserAwareAPIConsumer.java:86)
at org.wso2.carbon.apimgt.impl.UserAwareAPIConsumer.addApplication(UserAwareAPIConsumer.java:84)
at org.wso2.carbon.apimgt.rest.api.store.v1.impl.ApplicationsApiServiceImpl.applicationsPost(ApplicationsApiServiceImpl.java:182)
at org.wso2.carbon.apimgt.rest.api.store.v1.ApplicationsApi.applicationsPost(ApplicationsApi.java:451)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.apache.cxf.service.invoker.AbstractInvoker.performInvocation(AbstractInvoker.java:179)
at org.apache.cxf.service.invoker.AbstractInvoker.invoke(AbstractInvoker.java:96)
at org.apache.cxf.jaxrs.JAXRSInvoker.invoke(JAXRSInvoker.java:193)
at org.apache.cxf.jaxrs.JAXRSInvoker.invoke(JAXRSInvoker.java:103)
at org.apache.cxf.interceptor.ServiceInvokerInterceptor$1.run(ServiceInvokerInterceptor.java:59)
at org.apache.cxf.interceptor.ServiceInvokerInterceptor.handleMessage(ServiceInvokerInterceptor.java:96)
at org.apache.cxf.phase.PhaseInterceptorChain.doIntercept(PhaseInterceptorChain.java:308)
at org.apache.cxf.transport.ChainInitiationObserver.onMessage(ChainInitiationObserver.java:121)
at org.apache.cxf.transport.http.AbstractHTTPDestination.invoke(AbstractHTTPDestination.java:267)
at org.apache.cxf.transport.servlet.ServletController.invokeDestination(ServletController.java:234)
at org.apache.cxf.transport.servlet.ServletController.invoke(ServletController.java:208)
at org.apache.cxf.transport.servlet.ServletController.invoke(ServletController.java:160)
at org.apache.cxf.transport.servlet.CXFNonSpringServlet.invoke(CXFNonSpringServlet.java:216)
at org.apache.cxf.transport.servlet.AbstractHTTPServlet.handleRequest(AbstractHTTPServlet.java:301)
at org.apache.cxf.transport.servlet.AbstractHTTPServlet.doPost(AbstractHTTPServlet.java:220)
at javax.servlet.http.HttpServlet.service(HttpServlet.java:660)
at org.apache.cxf.transport.servlet.AbstractHTTPServlet.service(AbstractHTTPServlet.java:276)
at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:231)
at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:166)
at org.apache.tomcat.websocket.server.WsFilter.doFilter(WsFilter.java:53)
at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:193)
at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:166)
at org.apache.catalina.core.StandardWrapperValve.invoke(StandardWrapperValve.java:202)
at org.apache.catalina.core.StandardContextValve.invoke(StandardContextValve.java:96)
at org.apache.catalina.authenticator.AuthenticatorBase.invoke(AuthenticatorBase.java:541)
at org.apache.catalina.core.StandardHostValve.invoke(StandardHostValve.java:139)
at org.apache.catalina.valves.ErrorReportValve.invoke(ErrorReportValve.java:92)
at org.wso2.carbon.identity.context.rewrite.valve.TenantContextRewriteValve.invoke(TenantContextRewriteValve.java:86)
at org.wso2.carbon.identity.authz.valve.AuthorizationValve.invoke(AuthorizationValve.java:110)
at org.wso2.carbon.identity.auth.valve.AuthenticationValve.invoke(AuthenticationValve.java:75)
at org.wso2.carbon.tomcat.ext.valves.CompositeValve.continueInvocation(CompositeValve.java:99)
at org.wso2.carbon.tomcat.ext.valves.TomcatValveContainer.invokeValves(TomcatValveContainer.java:49)
at org.wso2.carbon.tomcat.ext.valves.CompositeValve.invoke(CompositeValve.java:62)
at org.wso2.carbon.tomcat.ext.valves.CarbonStuckThreadDetectionValve.invoke(CarbonStuckThreadDetectionValve.java:145)
at org.apache.catalina.valves.AbstractAccessLogValve.invoke(AbstractAccessLogValve.java:688)
at org.wso2.carbon.tomcat.ext.valves.CarbonContextCreatorValve.invoke(CarbonContextCreatorValve.java:57)
at org.wso2.carbon.tomcat.ext.valves.RequestCorrelationIdValve.invoke(RequestCorrelationIdValve.java:119)
at org.apache.catalina.core.StandardEngineValve.invoke(StandardEngineValve.java:74)
at org.apache.catalina.connector.CoyoteAdapter.service(CoyoteAdapter.java:343)
at org.apache.coyote.http11.Http11Processor.service(Http11Processor.java:367)
at org.apache.coyote.AbstractProcessorLight.process(AbstractProcessorLight.java:65)
at org.apache.coyote.AbstractProtocol$ConnectionHandler.process(AbstractProtocol.java:868)
at org.apache.tomcat.util.net.NioEndpoint$SocketProcessor.doRun(NioEndpoint.java:1639)
at org.apache.tomcat.util.net.SocketProcessorBase.run(SocketProcessorBase.java:49)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
at org.apache.tomcat.util.threads.TaskThread$WrappingRunnable.run(TaskThread.java:61)
at java.lang.Thread.run(Thread.java:748)
TID: [-1234] [api/am/store] [2020-08-08 21:57:02,063] ERROR {org.wso2.carbon.apimgt.rest.api.store.v1.impl.ApplicationsApiServiceImpl} - Error while adding a new application for the user admin org.wso2.carbon.apimgt.api.APIManagementException: Failed to add Application
at org.wso2.carbon.apimgt.impl.dao.ApiMgtDAO.handleException_aroundBody320(ApiMgtDAO.java:7297)
at org.wso2.carbon.apimgt.impl.dao.ApiMgtDAO.handleException(ApiMgtDAO.java:7295)
at org.wso2.carbon.apimgt.impl.dao.ApiMgtDAO.addApplication_aroundBody186(ApiMgtDAO.java:4065)
{code} | non_defect | error while creating an application when giving some long description description unable to create an application with a long description in the ui level it is not limiting restricting the length steps to reproduce try to create an application with long description affected product version apim environment details with versions os mac os code xml tid error org carbon apimgt impl dao apimgtdao failed to add application org jdbc jdbcsqldataexception value too long for column description varchar my abic test application my abic test application abic test application my abic test appli sql statement insert into am application name subscriber id application tier callback url description application status group id created by created time updated time uuid token type values at org message dbexception getjdbcsqlexception dbexception java at org message dbexception getjdbcsqlexception dbexception java at org message dbexception get dbexception java at org table column validateconvertupdatesequence column java at org table table validateconvertupdatesequence table java at org command dml insert insertrows insert java at org command dml insert update insert java at org command commandcontainer update commandcontainer java at org command command executeupdate command java at org jdbc jdbcpreparedstatement executeupdateinternal jdbcpreparedstatement java at org jdbc jdbcpreparedstatement executeupdate jdbcpreparedstatement java at sun reflect invoke unknown source at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org apache tomcat jdbc pool statementfacade statementproxy invoke statementfacade java at com sun proxy executeupdate unknown source at org carbon apimgt impl dao apimgtdao addapplication apimgtdao java at org carbon apimgt impl dao apimgtdao addapplication apimgtdao java at org carbon apimgt impl dao apimgtdao addapplication apimgtdao java at org carbon apimgt impl dao apimgtdao addapplication apimgtdao java at org carbon apimgt impl apiconsumerimpl addapplication apiconsumerimpl java at org carbon apimgt impl apiconsumerimpl addapplication apiconsumerimpl java at org carbon apimgt impl userawareapiconsumer addapplication userawareapiconsumer java at org carbon apimgt impl userawareapiconsumer addapplication userawareapiconsumer java at org carbon apimgt rest api store impl applicationsapiserviceimpl applicationspost applicationsapiserviceimpl java at org carbon apimgt rest api store applicationsapi applicationspost applicationsapi java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org apache cxf service invoker abstractinvoker performinvocation abstractinvoker java at org apache cxf service invoker abstractinvoker invoke abstractinvoker java at org apache cxf jaxrs jaxrsinvoker invoke jaxrsinvoker java at org apache cxf jaxrs jaxrsinvoker invoke jaxrsinvoker java at org apache cxf interceptor serviceinvokerinterceptor run serviceinvokerinterceptor java at org apache cxf interceptor serviceinvokerinterceptor handlemessage serviceinvokerinterceptor java at org apache cxf phase phaseinterceptorchain dointercept phaseinterceptorchain java at org apache cxf transport chaininitiationobserver onmessage chaininitiationobserver java at org apache cxf transport http abstracthttpdestination invoke abstracthttpdestination java at org apache cxf transport servlet servletcontroller invokedestination servletcontroller java at org apache cxf transport servlet servletcontroller invoke servletcontroller java at org apache cxf transport servlet servletcontroller invoke servletcontroller java at org apache cxf transport servlet cxfnonspringservlet invoke cxfnonspringservlet java at org apache cxf transport servlet abstracthttpservlet handlerequest abstracthttpservlet java at org apache cxf transport servlet abstracthttpservlet dopost abstracthttpservlet java at javax servlet http httpservlet service httpservlet java at org apache cxf transport servlet abstracthttpservlet service abstracthttpservlet java at org apache catalina core applicationfilterchain internaldofilter applicationfilterchain java at org apache catalina core applicationfilterchain dofilter applicationfilterchain java at org apache tomcat websocket server wsfilter dofilter wsfilter java at org apache catalina core applicationfilterchain internaldofilter applicationfilterchain java at org apache catalina core applicationfilterchain dofilter applicationfilterchain java at org apache catalina core standardwrappervalve invoke standardwrappervalve java at org apache catalina core standardcontextvalve invoke standardcontextvalve java at org apache catalina authenticator authenticatorbase invoke authenticatorbase java at org apache catalina core standardhostvalve invoke standardhostvalve java at org apache catalina valves errorreportvalve invoke errorreportvalve java at org carbon identity context rewrite valve tenantcontextrewritevalve invoke tenantcontextrewritevalve java at org carbon identity authz valve authorizationvalve invoke authorizationvalve java at org carbon identity auth valve authenticationvalve invoke authenticationvalve java at org carbon tomcat ext valves compositevalve continueinvocation compositevalve java at org carbon tomcat ext valves tomcatvalvecontainer invokevalves tomcatvalvecontainer java at org carbon tomcat ext valves compositevalve invoke compositevalve java at org carbon tomcat ext valves carbonstuckthreaddetectionvalve invoke carbonstuckthreaddetectionvalve java at org apache catalina valves abstractaccesslogvalve invoke abstractaccesslogvalve java at org carbon tomcat ext valves carboncontextcreatorvalve invoke carboncontextcreatorvalve java at org carbon tomcat ext valves requestcorrelationidvalve invoke requestcorrelationidvalve java at org apache catalina core standardenginevalve invoke standardenginevalve java at org apache catalina connector coyoteadapter service coyoteadapter java at org apache coyote service java at org apache coyote abstractprocessorlight process abstractprocessorlight java at org apache coyote abstractprotocol connectionhandler process abstractprotocol java at org apache tomcat util net nioendpoint socketprocessor dorun nioendpoint java at org apache tomcat util net socketprocessorbase run socketprocessorbase java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at org apache tomcat util threads taskthread wrappingrunnable run taskthread java at java lang thread run thread java tid error org carbon apimgt rest api store impl applicationsapiserviceimpl error while adding a new application for the user admin org carbon apimgt api apimanagementexception failed to add application at org carbon apimgt impl dao apimgtdao handleexception apimgtdao java at org carbon apimgt impl dao apimgtdao handleexception apimgtdao java at org carbon apimgt impl dao apimgtdao addapplication apimgtdao java code | 0 |
180,099 | 21,625,488,819 | IssuesEvent | 2022-05-05 01:08:44 | vipinsun/fabric-sdk-go | https://api.github.com/repos/vipinsun/fabric-sdk-go | opened | CVE-2022-25647 (High) detected in gson-2.7.jar | security vulnerability | ## CVE-2022-25647 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>gson-2.7.jar</b></p></summary>
<p>Gson JSON library</p>
<p>Library home page: <a href="https://github.com/google/gson">https://github.com/google/gson</a></p>
<p>Path to dependency file: /test/fixtures/testdata/java/example_cc/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.code.gson/gson/2.7/751f548c85fa49f330cecbb1875893f971b33c4e/gson-2.7.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.code.gson/gson/2.7/751f548c85fa49f330cecbb1875893f971b33c4e/gson-2.7.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.code.gson/gson/2.7/751f548c85fa49f330cecbb1875893f971b33c4e/gson-2.7.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.code.gson/gson/2.7/751f548c85fa49f330cecbb1875893f971b33c4e/gson-2.7.jar</p>
<p>
Dependency Hierarchy:
- fabric-chaincode-shim-1.4.8.jar (Root Library)
- fabric-chaincode-protos-1.4.8.jar
- protobuf-java-util-3.5.1.jar
- :x: **gson-2.7.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vipinsun/fabric-sdk-go/commit/432a85aa9d4094d52823bdb4be9cf19758df85e1">432a85aa9d4094d52823bdb4be9cf19758df85e1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package com.google.code.gson:gson before 2.8.9 are vulnerable to Deserialization of Untrusted Data via the writeReplace() method in internal classes, which may lead to DoS attacks.
<p>Publish Date: 2022-05-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-25647>CVE-2022-25647</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25647`">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25647`</a></p>
<p>Release Date: 2022-05-01</p>
<p>Fix Resolution (com.google.code.gson:gson): 2.8.9</p>
<p>Direct dependency fix Resolution (org.hyperledger.fabric-chaincode-java:fabric-chaincode-shim): 2.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-25647 (High) detected in gson-2.7.jar - ## CVE-2022-25647 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>gson-2.7.jar</b></p></summary>
<p>Gson JSON library</p>
<p>Library home page: <a href="https://github.com/google/gson">https://github.com/google/gson</a></p>
<p>Path to dependency file: /test/fixtures/testdata/java/example_cc/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.code.gson/gson/2.7/751f548c85fa49f330cecbb1875893f971b33c4e/gson-2.7.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.code.gson/gson/2.7/751f548c85fa49f330cecbb1875893f971b33c4e/gson-2.7.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.code.gson/gson/2.7/751f548c85fa49f330cecbb1875893f971b33c4e/gson-2.7.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.code.gson/gson/2.7/751f548c85fa49f330cecbb1875893f971b33c4e/gson-2.7.jar</p>
<p>
Dependency Hierarchy:
- fabric-chaincode-shim-1.4.8.jar (Root Library)
- fabric-chaincode-protos-1.4.8.jar
- protobuf-java-util-3.5.1.jar
- :x: **gson-2.7.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vipinsun/fabric-sdk-go/commit/432a85aa9d4094d52823bdb4be9cf19758df85e1">432a85aa9d4094d52823bdb4be9cf19758df85e1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package com.google.code.gson:gson before 2.8.9 are vulnerable to Deserialization of Untrusted Data via the writeReplace() method in internal classes, which may lead to DoS attacks.
<p>Publish Date: 2022-05-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-25647>CVE-2022-25647</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25647`">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25647`</a></p>
<p>Release Date: 2022-05-01</p>
<p>Fix Resolution (com.google.code.gson:gson): 2.8.9</p>
<p>Direct dependency fix Resolution (org.hyperledger.fabric-chaincode-java:fabric-chaincode-shim): 2.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_defect | cve high detected in gson jar cve high severity vulnerability vulnerable library gson jar gson json library library home page a href path to dependency file test fixtures testdata java example cc build gradle path to vulnerable library home wss scanner gradle caches modules files com google code gson gson gson jar home wss scanner gradle caches modules files com google code gson gson gson jar home wss scanner gradle caches modules files com google code gson gson gson jar home wss scanner gradle caches modules files com google code gson gson gson jar dependency hierarchy fabric chaincode shim jar root library fabric chaincode protos jar protobuf java util jar x gson jar vulnerable library found in head commit a href found in base branch main vulnerability details the package com google code gson gson before are vulnerable to deserialization of untrusted data via the writereplace method in internal classes which may lead to dos attacks publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com google code gson gson direct dependency fix resolution org hyperledger fabric chaincode java fabric chaincode shim step up your open source security game with whitesource | 0 |
297,747 | 25,760,391,247 | IssuesEvent | 2022-12-08 19:58:46 | daisy/pipeline-ui | https://api.github.com/repos/daisy/pipeline-ui | closed | Close tab button title needs to include name of job that it will close | question tester-feedback | "When more than one tab has been opened, pressing the tab key moves the focus to “X” (close” button of other tabs and Jaws reads it as “close tab job new button”. The label should include the name of tab that will be closed. "
cc @prashantverma2014 | 1.0 | Close tab button title needs to include name of job that it will close - "When more than one tab has been opened, pressing the tab key moves the focus to “X” (close” button of other tabs and Jaws reads it as “close tab job new button”. The label should include the name of tab that will be closed. "
cc @prashantverma2014 | non_defect | close tab button title needs to include name of job that it will close when more than one tab has been opened pressing the tab key moves the focus to “x” close” button of other tabs and jaws reads it as “close tab job new button” the label should include the name of tab that will be closed cc | 0 |
14,978 | 5,843,300,938 | IssuesEvent | 2017-05-10 08:50:21 | tarantool/mysql | https://api.github.com/repos/tarantool/mysql | closed | Can't build with openssl 1.0.1k on Alpine 3.5 | build | ```
/rocks/mysql/mariadb-connector-c/libmariadb/secure/openssl.c: In function 'ma_tls_start':
/rocks/mysql/mariadb-connector-c/libmariadb/secure/openssl.c:291:8: warning: implicit declaration of function 'OPENSSL_init_ssl' [-Wimplicit-function-declaration]
if (!OPENSSL_init_ssl(OPENSSL_INIT_LOAD_CONFIG, NULL))
^~~~~~~~~~~~~~~~
/rocks/mysql/mariadb-connector-c/libmariadb/secure/openssl.c:291:25: error: 'OPENSSL_INIT_LOAD_CONFIG' undeclared (first use in this function)
if (!OPENSSL_init_ssl(OPENSSL_INIT_LOAD_CONFIG, NULL))
^~~~~~~~~~~~~~~~~~~~~~~~
/rocks/mysql/mariadb-connector-c/libmariadb/secure/openssl.c:291:25: note: each undeclared identifier is reported only once for each function it appears in
/rocks/mysql/mariadb-connector-c/libmariadb/secure/openssl.c: In function 'ma_tls_verify_server_cert':
/rocks/mysql/mariadb-connector-c/libmariadb/secure/openssl.c:675:20: warning: implicit declaration of function 'ASN1_STRING_get0_data' [-Wimplicit-function-declaration]
cn_str = (char *)ASN1_STRING_get0_data(cn_asn1);
^~~~~~~~~~~~~~~~~~~~~
/rocks/mysql/mariadb-connector-c/libmariadb/secure/openssl.c:675:12: warning: cast to pointer from integer of different size [-Wint-to-pointer-cast]
cn_str = (char *)ASN1_STRING_get0_data(cn_asn1);
^
make[2]: *** [mariadb-connector-c/libmariadb/CMakeFiles/mariadb_obj.dir/build.make:735: mariadb-connector-c/libmariadb/CMakeFiles/mariadb_obj.dir/secure/openssl.c.o] Error 1
make[1]: *** [CMakeFiles/Makefile2:237: mariadb-connector-c/libmariadb/CMakeFiles/mariadb_obj.dir/all] Error 2
make: *** [Makefile:150: all] Error 2
Error: Build error: Failed building.
``` | 1.0 | Can't build with openssl 1.0.1k on Alpine 3.5 - ```
/rocks/mysql/mariadb-connector-c/libmariadb/secure/openssl.c: In function 'ma_tls_start':
/rocks/mysql/mariadb-connector-c/libmariadb/secure/openssl.c:291:8: warning: implicit declaration of function 'OPENSSL_init_ssl' [-Wimplicit-function-declaration]
if (!OPENSSL_init_ssl(OPENSSL_INIT_LOAD_CONFIG, NULL))
^~~~~~~~~~~~~~~~
/rocks/mysql/mariadb-connector-c/libmariadb/secure/openssl.c:291:25: error: 'OPENSSL_INIT_LOAD_CONFIG' undeclared (first use in this function)
if (!OPENSSL_init_ssl(OPENSSL_INIT_LOAD_CONFIG, NULL))
^~~~~~~~~~~~~~~~~~~~~~~~
/rocks/mysql/mariadb-connector-c/libmariadb/secure/openssl.c:291:25: note: each undeclared identifier is reported only once for each function it appears in
/rocks/mysql/mariadb-connector-c/libmariadb/secure/openssl.c: In function 'ma_tls_verify_server_cert':
/rocks/mysql/mariadb-connector-c/libmariadb/secure/openssl.c:675:20: warning: implicit declaration of function 'ASN1_STRING_get0_data' [-Wimplicit-function-declaration]
cn_str = (char *)ASN1_STRING_get0_data(cn_asn1);
^~~~~~~~~~~~~~~~~~~~~
/rocks/mysql/mariadb-connector-c/libmariadb/secure/openssl.c:675:12: warning: cast to pointer from integer of different size [-Wint-to-pointer-cast]
cn_str = (char *)ASN1_STRING_get0_data(cn_asn1);
^
make[2]: *** [mariadb-connector-c/libmariadb/CMakeFiles/mariadb_obj.dir/build.make:735: mariadb-connector-c/libmariadb/CMakeFiles/mariadb_obj.dir/secure/openssl.c.o] Error 1
make[1]: *** [CMakeFiles/Makefile2:237: mariadb-connector-c/libmariadb/CMakeFiles/mariadb_obj.dir/all] Error 2
make: *** [Makefile:150: all] Error 2
Error: Build error: Failed building.
``` | non_defect | can t build with openssl on alpine rocks mysql mariadb connector c libmariadb secure openssl c in function ma tls start rocks mysql mariadb connector c libmariadb secure openssl c warning implicit declaration of function openssl init ssl if openssl init ssl openssl init load config null rocks mysql mariadb connector c libmariadb secure openssl c error openssl init load config undeclared first use in this function if openssl init ssl openssl init load config null rocks mysql mariadb connector c libmariadb secure openssl c note each undeclared identifier is reported only once for each function it appears in rocks mysql mariadb connector c libmariadb secure openssl c in function ma tls verify server cert rocks mysql mariadb connector c libmariadb secure openssl c warning implicit declaration of function string data cn str char string data cn rocks mysql mariadb connector c libmariadb secure openssl c warning cast to pointer from integer of different size cn str char string data cn make error make error make error error build error failed building | 0 |
35,158 | 7,620,288,877 | IssuesEvent | 2018-05-03 01:43:03 | CyberKoz/project-management-demonstration | https://api.github.com/repos/CyberKoz/project-management-demonstration | closed | Defect: The homepage doesn't work | High defect workaround-approved | Can not log into the Home Page
Test case #4
Found in: 99645506111641b8f1f15881db23d56854deb7b7 | 1.0 | Defect: The homepage doesn't work - Can not log into the Home Page
Test case #4
Found in: 99645506111641b8f1f15881db23d56854deb7b7 | defect | defect the homepage doesn t work can not log into the home page test case found in | 1 |
10,386 | 2,622,149,328 | IssuesEvent | 2015-03-04 00:05:27 | byzhang/cuda-convnet2 | https://api.github.com/repos/byzhang/cuda-convnet2 | opened | Does not work on 8 GPUs | auto-migrated Priority-Medium Type-Defect | ```
I have some problems running this code on 8 gpus. It crashed at the line:
assert(same.size() == 3); in reducepipeline.cu
What steps will reproduce the problem?
1. get 8 k40 gpu, install them in 2 PCI buses. 4 for each.
2. train with 512 mini batch, data parallelism.
```
Original issue reported on code.google.com by `wangmeng...@gmail.com` on 3 Oct 2014 at 5:04 | 1.0 | Does not work on 8 GPUs - ```
I have some problems running this code on 8 gpus. It crashed at the line:
assert(same.size() == 3); in reducepipeline.cu
What steps will reproduce the problem?
1. get 8 k40 gpu, install them in 2 PCI buses. 4 for each.
2. train with 512 mini batch, data parallelism.
```
Original issue reported on code.google.com by `wangmeng...@gmail.com` on 3 Oct 2014 at 5:04 | defect | does not work on gpus i have some problems running this code on gpus it crashed at the line assert same size in reducepipeline cu what steps will reproduce the problem get gpu install them in pci buses for each train with mini batch data parallelism original issue reported on code google com by wangmeng gmail com on oct at | 1 |
477,824 | 13,768,921,205 | IssuesEvent | 2020-10-07 17:48:53 | zephyrproject-rtos/zephyr | https://api.github.com/repos/zephyrproject-rtos/zephyr | opened | [Coverity CID :214873] Argument cannot be negative in tests/posix/eventfd/src/main.c | Coverity bug priority: low |
Static code scan issues found in file:
https://github.com/zephyrproject-rtos/zephyr/tree/master/tests/posix/eventfd/src/main.c
Category: Error handling issues
Function: `test_eventfd_unset_poll_event_nonblock`
Component: Tests
CID: [214873](https://scan9.coverity.com/reports.htm#v29726/p12996/mergedDefectId=214873)
Please fix or provide comments in coverity using the link:
https://scan9.coverity.com/reports.htm#v32951/p12996.
Note: This issue was created automatically. Priority was set based on classification
of the file affected and the impact field in coverity. Assignees were set using the CODEOWNERS file.
| 1.0 | [Coverity CID :214873] Argument cannot be negative in tests/posix/eventfd/src/main.c -
Static code scan issues found in file:
https://github.com/zephyrproject-rtos/zephyr/tree/master/tests/posix/eventfd/src/main.c
Category: Error handling issues
Function: `test_eventfd_unset_poll_event_nonblock`
Component: Tests
CID: [214873](https://scan9.coverity.com/reports.htm#v29726/p12996/mergedDefectId=214873)
Please fix or provide comments in coverity using the link:
https://scan9.coverity.com/reports.htm#v32951/p12996.
Note: This issue was created automatically. Priority was set based on classification
of the file affected and the impact field in coverity. Assignees were set using the CODEOWNERS file.
| non_defect | argument cannot be negative in tests posix eventfd src main c static code scan issues found in file category error handling issues function test eventfd unset poll event nonblock component tests cid please fix or provide comments in coverity using the link note this issue was created automatically priority was set based on classification of the file affected and the impact field in coverity assignees were set using the codeowners file | 0 |
53,475 | 13,168,569,485 | IssuesEvent | 2020-08-11 12:21:53 | mozilla-mobile/fenix | https://api.github.com/repos/mozilla-mobile/fenix | reopened | FNX2-15483 ⁃ [Bug] Weird Glean Sentry crashes suggesting code is being optimized away | b:crash eng:build 🐞 bug | We've been seeing a few bunch of weird Sentry issues recently:
* [Null reference used for synchronization](https://sentry.prod.mozaws.net/operations/fenix-nightly/issues/9086498/?query=is%3Aunresolved%20glean)
* [Class 'java.lang.VirtualMachineError' does not implement interface ...](https://sentry.prod.mozaws.net/operations/fenix/issues/9163643/?query=is%3Aunresolved%20glean)
Both stacktraces look really weird and seem to suggest that code is being optimized away by R8, breaking some builds in a very nasty way.
@NotWoods was looking into something similar in the past few weeks-
| 1.0 | FNX2-15483 ⁃ [Bug] Weird Glean Sentry crashes suggesting code is being optimized away - We've been seeing a few bunch of weird Sentry issues recently:
* [Null reference used for synchronization](https://sentry.prod.mozaws.net/operations/fenix-nightly/issues/9086498/?query=is%3Aunresolved%20glean)
* [Class 'java.lang.VirtualMachineError' does not implement interface ...](https://sentry.prod.mozaws.net/operations/fenix/issues/9163643/?query=is%3Aunresolved%20glean)
Both stacktraces look really weird and seem to suggest that code is being optimized away by R8, breaking some builds in a very nasty way.
@NotWoods was looking into something similar in the past few weeks-
| non_defect | ⁃ weird glean sentry crashes suggesting code is being optimized away we ve been seeing a few bunch of weird sentry issues recently both stacktraces look really weird and seem to suggest that code is being optimized away by breaking some builds in a very nasty way notwoods was looking into something similar in the past few weeks | 0 |
31,873 | 2,740,651,870 | IssuesEvent | 2015-04-21 04:29:39 | mpiannucci/HackWinds-Android | https://api.github.com/repos/mpiannucci/HackWinds-Android | closed | Fix broken forecast change notifications. | bug High Priority | For some reason nothing is updating. Shouldn't be too comlicated | 1.0 | Fix broken forecast change notifications. - For some reason nothing is updating. Shouldn't be too comlicated | non_defect | fix broken forecast change notifications for some reason nothing is updating shouldn t be too comlicated | 0 |
305,458 | 26,390,712,846 | IssuesEvent | 2023-01-12 15:29:24 | CSOIreland/PxStat | https://api.github.com/repos/CSOIreland/PxStat | closed | [BUG] Search returns multiple copies of the same table | bug released tested fixed | **Describe the bug**
Search returns multiple copies of the same table
**To Reproduce**
Steps to reproduce the behavior in dev
1. Do a search for Transport
2. Limit the view by properties for easier viewing
**Expected behavior**
A single example of each table in the search
**Screenshots**
| 1.0 | [BUG] Search returns multiple copies of the same table - **Describe the bug**
Search returns multiple copies of the same table
**To Reproduce**
Steps to reproduce the behavior in dev
1. Do a search for Transport
2. Limit the view by properties for easier viewing
**Expected behavior**
A single example of each table in the search
**Screenshots**
| non_defect | search returns multiple copies of the same table describe the bug search returns multiple copies of the same table to reproduce steps to reproduce the behavior in dev do a search for transport limit the view by properties for easier viewing expected behavior a single example of each table in the search screenshots | 0 |
17,857 | 3,013,540,504 | IssuesEvent | 2015-07-29 09:36:47 | yawlfoundation/yawl | https://api.github.com/repos/yawlfoundation/yawl | closed | Default values for task output variables are not implemented | auto-migrated Priority-Medium Type-Defect | ```
As discussed with Michael, you can set default values for task output only
variables (cf. initial values for net vars), but these are never used.
I presume that the better solution is only to use them if *no* element is
returned, rather than an empty one <anElement />. (The latter would be OK for a
return var with a type containing all optional minOccurs="0" elements.)
Setting status Accepted due to previous discussion.
```
Original issue reported on code.google.com by `monsieur...@gmail.com` on 11 Feb 2011 at 4:21 | 1.0 | Default values for task output variables are not implemented - ```
As discussed with Michael, you can set default values for task output only
variables (cf. initial values for net vars), but these are never used.
I presume that the better solution is only to use them if *no* element is
returned, rather than an empty one <anElement />. (The latter would be OK for a
return var with a type containing all optional minOccurs="0" elements.)
Setting status Accepted due to previous discussion.
```
Original issue reported on code.google.com by `monsieur...@gmail.com` on 11 Feb 2011 at 4:21 | defect | default values for task output variables are not implemented as discussed with michael you can set default values for task output only variables cf initial values for net vars but these are never used i presume that the better solution is only to use them if no element is returned rather than an empty one the latter would be ok for a return var with a type containing all optional minoccurs elements setting status accepted due to previous discussion original issue reported on code google com by monsieur gmail com on feb at | 1 |
68,863 | 21,931,742,463 | IssuesEvent | 2022-05-23 10:20:00 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | Live location sharing map copyright attribution overlaps with beacon status bar in timeline tile | T-Defect S-Tolerable O-Occasional Z-Labs A-Location-Sharing | ### Steps to reproduce
1. Start live location sharing
2. Live location appears in timeline
### Outcome
#### What did you expect?
(i) icon above status bar
#### What happened instead?
(i) icon is behind the status bar

### Operating system
Ubuntu 22.04 LTS
### Browser information
Firefox 100.0
### URL for webapp
https://develop.element.io/
### Application version
Version von Element: 88b5368f7254-react-5f8aecaf08e5-js-f44510e65f9b Version von Olm: 3.2.8
### Homeserver
_No response_
### Will you send logs?
No | 1.0 | Live location sharing map copyright attribution overlaps with beacon status bar in timeline tile - ### Steps to reproduce
1. Start live location sharing
2. Live location appears in timeline
### Outcome
#### What did you expect?
(i) icon above status bar
#### What happened instead?
(i) icon is behind the status bar

### Operating system
Ubuntu 22.04 LTS
### Browser information
Firefox 100.0
### URL for webapp
https://develop.element.io/
### Application version
Version von Element: 88b5368f7254-react-5f8aecaf08e5-js-f44510e65f9b Version von Olm: 3.2.8
### Homeserver
_No response_
### Will you send logs?
No | defect | live location sharing map copyright attribution overlaps with beacon status bar in timeline tile steps to reproduce start live location sharing live location appears in timeline outcome what did you expect i icon above status bar what happened instead i icon is behind the status bar operating system ubuntu lts browser information firefox url for webapp application version version von element react js version von olm homeserver no response will you send logs no | 1 |
262,776 | 8,272,473,894 | IssuesEvent | 2018-09-16 20:33:10 | javaee/glassfish | https://api.github.com/repos/javaee/glassfish | closed | Remove requirement to restart DAS and instances when enabling/disabling secure admin | Component: admin Priority: Major Type: Improvement ee7ri_cleanup_deferred | Currently we instruct users to stop non-DAS instances, leaving only the DAS running, when running enable/disable-secure-admin.
Ideally, users could enable and disable secure admin without having to stop remote instances and then restarting the DAS and the remote instances.
#### Affected Versions
[3.1_dev] | 1.0 | Remove requirement to restart DAS and instances when enabling/disabling secure admin - Currently we instruct users to stop non-DAS instances, leaving only the DAS running, when running enable/disable-secure-admin.
Ideally, users could enable and disable secure admin without having to stop remote instances and then restarting the DAS and the remote instances.
#### Affected Versions
[3.1_dev] | non_defect | remove requirement to restart das and instances when enabling disabling secure admin currently we instruct users to stop non das instances leaving only the das running when running enable disable secure admin ideally users could enable and disable secure admin without having to stop remote instances and then restarting the das and the remote instances affected versions | 0 |
13,605 | 2,772,490,147 | IssuesEvent | 2015-05-02 18:34:47 | holocronweaver/accidental-noise-library | https://api.github.com/repos/holocronweaver/accidental-noise-library | closed | CImplicitScaleDomain? | auto-migrated Priority-Medium Type-Defect | ```
Hi,
How does someone use that function? I see lots of overloaded definitions in the
headers.
Thanks
Colin
```
Original issue reported on code.google.com by `colingil...@gmail.com` on 4 Apr 2015 at 5:29 | 1.0 | CImplicitScaleDomain? - ```
Hi,
How does someone use that function? I see lots of overloaded definitions in the
headers.
Thanks
Colin
```
Original issue reported on code.google.com by `colingil...@gmail.com` on 4 Apr 2015 at 5:29 | defect | cimplicitscaledomain hi how does someone use that function i see lots of overloaded definitions in the headers thanks colin original issue reported on code google com by colingil gmail com on apr at | 1 |
244,725 | 18,766,557,768 | IssuesEvent | 2021-11-06 02:36:55 | AY2122S1-CS2113T-F11-4/tp | https://api.github.com/repos/AY2122S1-CS2113T-F11-4/tp | closed | update UG for the edit command property input | type.Documentation | edit command property input now is any property from the {purchase cost, selling price, remarks} set. | 1.0 | update UG for the edit command property input - edit command property input now is any property from the {purchase cost, selling price, remarks} set. | non_defect | update ug for the edit command property input edit command property input now is any property from the purchase cost selling price remarks set | 0 |
71,758 | 7,255,894,524 | IssuesEvent | 2018-02-16 16:17:13 | openPMD/openPMD-api | https://api.github.com/repos/openPMD/openPMD-api | closed | ParalleIOTest failing | MPI bug tests | @C0nsultant currently, the `ParalleIOTest.cpp` does not compile.
Issues are:
- access to the `Series()` object
- changed API of the `loadChunk()` member function.
I think the first issue is solvable via
```diff
diff --git a/test/ParallelIOTest.cpp b/test/ParallelIOTest.cpp
index cef531f..b45c9e6 100755
--- a/test/ParallelIOTest.cpp
+++ b/test/ParallelIOTest.cpp
@@ -35,9 +35,9 @@ BOOST_AUTO_TEST_CASE(git_hdf5_sample_content_test)
MPI_Comm_rank(MPI_COMM_WORLD, &mpi_rank);
/* only a 3x3x3 chunk of the actual data is hardcoded. every worker reads 1/3 */
uint64_t rank = mpi_rank % 3;
- Series o = Series("../samples/git-sample/",
- "data00000%T.h5",
- true);
+ Series o = Series::read("../samples/git-sample/",
+ "data00000%T.h5",
+ true);
{
```
Can you please provide a PR that fixes the test? | 1.0 | ParalleIOTest failing - @C0nsultant currently, the `ParalleIOTest.cpp` does not compile.
Issues are:
- access to the `Series()` object
- changed API of the `loadChunk()` member function.
I think the first issue is solvable via
```diff
diff --git a/test/ParallelIOTest.cpp b/test/ParallelIOTest.cpp
index cef531f..b45c9e6 100755
--- a/test/ParallelIOTest.cpp
+++ b/test/ParallelIOTest.cpp
@@ -35,9 +35,9 @@ BOOST_AUTO_TEST_CASE(git_hdf5_sample_content_test)
MPI_Comm_rank(MPI_COMM_WORLD, &mpi_rank);
/* only a 3x3x3 chunk of the actual data is hardcoded. every worker reads 1/3 */
uint64_t rank = mpi_rank % 3;
- Series o = Series("../samples/git-sample/",
- "data00000%T.h5",
- true);
+ Series o = Series::read("../samples/git-sample/",
+ "data00000%T.h5",
+ true);
{
```
Can you please provide a PR that fixes the test? | non_defect | paralleiotest failing currently the paralleiotest cpp does not compile issues are access to the series object changed api of the loadchunk member function i think the first issue is solvable via diff diff git a test paralleliotest cpp b test paralleliotest cpp index a test paralleliotest cpp b test paralleliotest cpp boost auto test case git sample content test mpi comm rank mpi comm world mpi rank only a chunk of the actual data is hardcoded every worker reads t rank mpi rank series o series samples git sample t true series o series read samples git sample t true can you please provide a pr that fixes the test | 0 |
193,330 | 15,374,270,245 | IssuesEvent | 2021-03-02 13:38:33 | glific/docs | https://api.github.com/repos/glific/docs | closed | Contact response type | documentation | @pankaj-ag @abhi1203 Assign this document to you for review. Let me know if you have feedback or suggestions.
**Contact response type**
https://glific.slab.com/posts/contact-response-type-dvuebrx0 | 1.0 | Contact response type - @pankaj-ag @abhi1203 Assign this document to you for review. Let me know if you have feedback or suggestions.
**Contact response type**
https://glific.slab.com/posts/contact-response-type-dvuebrx0 | non_defect | contact response type pankaj ag assign this document to you for review let me know if you have feedback or suggestions contact response type | 0 |
468,453 | 13,483,259,782 | IssuesEvent | 2020-09-11 03:29:10 | tjcsl/ion | https://api.github.com/repos/tjcsl/ion | closed | Feedback when pressing button for forward email | area/ui priority/high type/enhancement type/feature | ## Feature description
Currently, there is no feedback for the "forward email" button. As it is pressed, there is no message that says "processing."
## Rationale for adding feature
Many people are spamming the button until it works or fails, which is bad.
## Suggested implementation(s) (if applicable)
- Possibly handle it similarly to Ion's login button? (where the button swaps with a spinner)
- Disable the button while Ion is waiting a response | 1.0 | Feedback when pressing button for forward email - ## Feature description
Currently, there is no feedback for the "forward email" button. As it is pressed, there is no message that says "processing."
## Rationale for adding feature
Many people are spamming the button until it works or fails, which is bad.
## Suggested implementation(s) (if applicable)
- Possibly handle it similarly to Ion's login button? (where the button swaps with a spinner)
- Disable the button while Ion is waiting a response | non_defect | feedback when pressing button for forward email feature description currently there is no feedback for the forward email button as it is pressed there is no message that says processing rationale for adding feature many people are spamming the button until it works or fails which is bad suggested implementation s if applicable possibly handle it similarly to ion s login button where the button swaps with a spinner disable the button while ion is waiting a response | 0 |
6,439 | 3,388,144,581 | IssuesEvent | 2015-11-29 01:38:12 | Modi777/Movie-File-Merger | https://api.github.com/repos/Modi777/Movie-File-Merger | closed | Add setting for default action on double click | Code Enhancement | Add a setting to choose what will happen after a double click. | 1.0 | Add setting for default action on double click - Add a setting to choose what will happen after a double click. | non_defect | add setting for default action on double click add a setting to choose what will happen after a double click | 0 |
64,685 | 18,795,957,045 | IssuesEvent | 2021-11-08 22:21:36 | sillsdev/StoryProducer | https://api.github.com/repos/sillsdev/StoryProducer | opened | Wordlinks quick fix for text back translation | Usability Defect | Swap out the place holder text on the Wordlinks audio file name:
WordLinks 1 --> **Press to back translate**
If the editable text box that comes up when the wordlinks1 audio file is pressed is separate from the editable text boxes used in other phases, please change the text to be this:
Choose a new name ---> **For key terms, type a word-for-word back translation. For names, spell the name in your language.** (long place holder text)
**Type a back translation or spell the name.** (short place holder text)
| 1.0 | Wordlinks quick fix for text back translation - Swap out the place holder text on the Wordlinks audio file name:
WordLinks 1 --> **Press to back translate**
If the editable text box that comes up when the wordlinks1 audio file is pressed is separate from the editable text boxes used in other phases, please change the text to be this:
Choose a new name ---> **For key terms, type a word-for-word back translation. For names, spell the name in your language.** (long place holder text)
**Type a back translation or spell the name.** (short place holder text)
| defect | wordlinks quick fix for text back translation swap out the place holder text on the wordlinks audio file name wordlinks press to back translate if the editable text box that comes up when the audio file is pressed is separate from the editable text boxes used in other phases please change the text to be this choose a new name for key terms type a word for word back translation for names spell the name in your language long place holder text type a back translation or spell the name short place holder text | 1 |
14,926 | 2,831,390,471 | IssuesEvent | 2015-05-24 15:55:19 | nobodyguy/dslrdashboard | https://api.github.com/repos/nobodyguy/dslrdashboard | closed | D800e not recognized | auto-migrated Priority-Medium Type-Defect | ```
I am connecting D800e using this OTG adapter:
http://www.newegg.com/Product/Product.aspx?Item=9SIA07R0FC9782 and using Asus
TF201 tablet with JellyBean and dslrdashboard V0.30.12.
Camera is not recognized. Any suggestions?
```
Original issue reported on code.google.com by `michaelezra000` on 8 Dec 2012 at 6:25 | 1.0 | D800e not recognized - ```
I am connecting D800e using this OTG adapter:
http://www.newegg.com/Product/Product.aspx?Item=9SIA07R0FC9782 and using Asus
TF201 tablet with JellyBean and dslrdashboard V0.30.12.
Camera is not recognized. Any suggestions?
```
Original issue reported on code.google.com by `michaelezra000` on 8 Dec 2012 at 6:25 | defect | not recognized i am connecting using this otg adapter and using asus tablet with jellybean and dslrdashboard camera is not recognized any suggestions original issue reported on code google com by on dec at | 1 |
51,701 | 13,211,286,291 | IssuesEvent | 2020-08-15 22:03:13 | icecube-trac/tix4 | https://api.github.com/repos/icecube-trac/tix4 | opened | clsim - Finish() has segfault if no frames processed (Trac #883) | Incomplete Migration Migrated from Trac combo simulation defect | <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/883">https://code.icecube.wisc.edu/projects/icecube/ticket/883</a>, reported by david.schultzand owned by olivas</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:15:08",
"_ts": "1550067308113782",
"description": "If you set up clsim, but don't give it any DAQ frames to process, the Finish() method will segfault.\n\nTest case:\n* make bottomless source\n* make clsim\n* Execute(1)\nboom - segfault\n\nThe specific error message is:\n{{{\npython: /scratch/dschultz/simulation/src/cmake/tool-patches/boost-1.38.0/boost\n/shared_ptr.hpp:421: T* boost::shared_ptr< <template-parameter-1-1> >::operato\nr->() const [with T = I3CLSimLightSourceToStepConverterGeant4]: Assertion `px \n!= 0' failed.\n}}}",
"reporter": "david.schultz",
"cc": "",
"resolution": "worksforme",
"time": "2015-02-23T22:47:15",
"component": "combo simulation",
"summary": "clsim - Finish() has segfault if no frames processed",
"priority": "minor",
"keywords": "clsim",
"milestone": "",
"owner": "olivas",
"type": "defect"
}
```
</p>
</details>
| 1.0 | clsim - Finish() has segfault if no frames processed (Trac #883) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/883">https://code.icecube.wisc.edu/projects/icecube/ticket/883</a>, reported by david.schultzand owned by olivas</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:15:08",
"_ts": "1550067308113782",
"description": "If you set up clsim, but don't give it any DAQ frames to process, the Finish() method will segfault.\n\nTest case:\n* make bottomless source\n* make clsim\n* Execute(1)\nboom - segfault\n\nThe specific error message is:\n{{{\npython: /scratch/dschultz/simulation/src/cmake/tool-patches/boost-1.38.0/boost\n/shared_ptr.hpp:421: T* boost::shared_ptr< <template-parameter-1-1> >::operato\nr->() const [with T = I3CLSimLightSourceToStepConverterGeant4]: Assertion `px \n!= 0' failed.\n}}}",
"reporter": "david.schultz",
"cc": "",
"resolution": "worksforme",
"time": "2015-02-23T22:47:15",
"component": "combo simulation",
"summary": "clsim - Finish() has segfault if no frames processed",
"priority": "minor",
"keywords": "clsim",
"milestone": "",
"owner": "olivas",
"type": "defect"
}
```
</p>
</details>
| defect | clsim finish has segfault if no frames processed trac migrated from json status closed changetime ts description if you set up clsim but don t give it any daq frames to process the finish method will segfault n ntest case n make bottomless source n make clsim n execute nboom segfault n nthe specific error message is n npython scratch dschultz simulation src cmake tool patches boost boost n shared ptr hpp t boost shared ptr operato nr const assertion px n failed n reporter david schultz cc resolution worksforme time component combo simulation summary clsim finish has segfault if no frames processed priority minor keywords clsim milestone owner olivas type defect | 1 |
88,287 | 8,137,358,399 | IssuesEvent | 2018-08-20 11:30:27 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | opened | Multiple failures on IBM JDK 7 | Team: Core Type: Test-Failure | *master* (commit 04783ec7754e5582d77e269663d08a3747aaefad)
We're getting multiple failures on IBM JDK 7. It looks suspicious that only in this specific platform we have many (19) failures from various tests. Tests that are failing:
om.hazelcast.client.impl.clientside.ClientDynamicClusterConfigTest.testCacheConfig
com.hazelcast.client.impl.clientside.ClientDynamicClusterConfigTest.testMapConfig_withQueryCacheConfig_andEntryListenerConfigByImplementation
com.hazelcast.client.impl.clientside.ClientDynamicClusterConfigTest.testReplicatedMapConfig_withListenerByClassName
com.hazelcast.client.impl.clientside.ClientDynamicClusterConfigTest.testSameReplicatedMapConfig_canBeAddedTwice
com.hazelcast.concurrent.lock.ConditionBasicDistributedTest.testAwaitExpiration_whenLockIsNotAcquired
com.hazelcast.concurrent.lock.ConditionBasicDistributedTest.testAwaitOnConditionOfFreeLock
com.hazelcast.concurrent.lock.ConditionBasicDistributedTest.testSignalWithMultipleWaiters
com.hazelcast.concurrent.lock.ConditionBasicDistributedTest.testConditionsWithSameNameButDifferentLocksAreIndependent
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.readOne
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.addAllAsync
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.addAsync_fail_whenNoSpace
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.addAsync_fail_whenSpace
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.addAsync_whenOverwrite_andNoTTL
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.size_whenSomeItemsAdded
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.sizeShouldNotExceedCapacity_whenPromotedFromBackup
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.destroy_whenBlockedThreads_thenDistributedObjectDestroyedException
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.addAllAsync_manyTimesRoundTheRing
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.readOne_whenTooFarAfterTail_thenIllegalArgumentException
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.addAsync_whenOverwrite_andTTL
Link to the Jenkins build: https://hazelcast-l337.ci.cloudbees.com/view/Official%20Builds/job/Hazelcast-3.x-IbmJDK7/234/ | 1.0 | Multiple failures on IBM JDK 7 - *master* (commit 04783ec7754e5582d77e269663d08a3747aaefad)
We're getting multiple failures on IBM JDK 7. It looks suspicious that only in this specific platform we have many (19) failures from various tests. Tests that are failing:
om.hazelcast.client.impl.clientside.ClientDynamicClusterConfigTest.testCacheConfig
com.hazelcast.client.impl.clientside.ClientDynamicClusterConfigTest.testMapConfig_withQueryCacheConfig_andEntryListenerConfigByImplementation
com.hazelcast.client.impl.clientside.ClientDynamicClusterConfigTest.testReplicatedMapConfig_withListenerByClassName
com.hazelcast.client.impl.clientside.ClientDynamicClusterConfigTest.testSameReplicatedMapConfig_canBeAddedTwice
com.hazelcast.concurrent.lock.ConditionBasicDistributedTest.testAwaitExpiration_whenLockIsNotAcquired
com.hazelcast.concurrent.lock.ConditionBasicDistributedTest.testAwaitOnConditionOfFreeLock
com.hazelcast.concurrent.lock.ConditionBasicDistributedTest.testSignalWithMultipleWaiters
com.hazelcast.concurrent.lock.ConditionBasicDistributedTest.testConditionsWithSameNameButDifferentLocksAreIndependent
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.readOne
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.addAllAsync
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.addAsync_fail_whenNoSpace
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.addAsync_fail_whenSpace
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.addAsync_whenOverwrite_andNoTTL
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.size_whenSomeItemsAdded
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.sizeShouldNotExceedCapacity_whenPromotedFromBackup
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.destroy_whenBlockedThreads_thenDistributedObjectDestroyedException
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.addAllAsync_manyTimesRoundTheRing
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.readOne_whenTooFarAfterTail_thenIllegalArgumentException
com.hazelcast.ringbuffer.impl.RingbufferBasicDistributedTest.addAsync_whenOverwrite_andTTL
Link to the Jenkins build: https://hazelcast-l337.ci.cloudbees.com/view/Official%20Builds/job/Hazelcast-3.x-IbmJDK7/234/ | non_defect | multiple failures on ibm jdk master commit we re getting multiple failures on ibm jdk it looks suspicious that only in this specific platform we have many failures from various tests tests that are failing om hazelcast client impl clientside clientdynamicclusterconfigtest testcacheconfig com hazelcast client impl clientside clientdynamicclusterconfigtest testmapconfig withquerycacheconfig andentrylistenerconfigbyimplementation com hazelcast client impl clientside clientdynamicclusterconfigtest testreplicatedmapconfig withlistenerbyclassname com hazelcast client impl clientside clientdynamicclusterconfigtest testsamereplicatedmapconfig canbeaddedtwice com hazelcast concurrent lock conditionbasicdistributedtest testawaitexpiration whenlockisnotacquired com hazelcast concurrent lock conditionbasicdistributedtest testawaitonconditionoffreelock com hazelcast concurrent lock conditionbasicdistributedtest testsignalwithmultiplewaiters com hazelcast concurrent lock conditionbasicdistributedtest testconditionswithsamenamebutdifferentlocksareindependent com hazelcast ringbuffer impl ringbufferbasicdistributedtest readone com hazelcast ringbuffer impl ringbufferbasicdistributedtest addallasync com hazelcast ringbuffer impl ringbufferbasicdistributedtest addasync fail whennospace com hazelcast ringbuffer impl ringbufferbasicdistributedtest addasync fail whenspace com hazelcast ringbuffer impl ringbufferbasicdistributedtest addasync whenoverwrite andnottl com hazelcast ringbuffer impl ringbufferbasicdistributedtest size whensomeitemsadded com hazelcast ringbuffer impl ringbufferbasicdistributedtest sizeshouldnotexceedcapacity whenpromotedfrombackup com hazelcast ringbuffer impl ringbufferbasicdistributedtest destroy whenblockedthreads thendistributedobjectdestroyedexception com hazelcast ringbuffer impl ringbufferbasicdistributedtest addallasync manytimesroundthering com hazelcast ringbuffer impl ringbufferbasicdistributedtest readone whentoofaraftertail thenillegalargumentexception com hazelcast ringbuffer impl ringbufferbasicdistributedtest addasync whenoverwrite andttl link to the jenkins build | 0 |
73,936 | 15,286,691,010 | IssuesEvent | 2021-02-23 14:58:43 | Baneeishaque/Android-Common-Utils4 | https://api.github.com/repos/Baneeishaque/Android-Common-Utils4 | opened | CVE-2018-1000180 (High) detected in bcprov-jdk15on-1.56.jar | security vulnerability | ## CVE-2018-1000180 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcprov-jdk15on-1.56.jar</b></p></summary>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptographic algorithms. This jar contains JCE provider and lightweight API for the Bouncy Castle Cryptography APIs for JDK 1.5 to JDK 1.8.</p>
<p>Library home page: <a href="http://www.bouncycastle.org/java.html">http://www.bouncycastle.org/java.html</a></p>
<p>Path to dependency file: Android-Common-Utils4/common4/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.bouncycastle/bcprov-jdk15on/1.56/a153c6f9744a3e9dd6feab5e210e1c9861362ec7/bcprov-jdk15on-1.56.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-27.1.2.jar (Root Library)
- sdk-common-27.1.2.jar
- :x: **bcprov-jdk15on-1.56.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Baneeishaque/Android-Common-Utils4/commit/e8328a1ad0239aaf16726916e083bb49de9642ec">e8328a1ad0239aaf16726916e083bb49de9642ec</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Bouncy Castle BC 1.54 - 1.59, BC-FJA 1.0.0, BC-FJA 1.0.1 and earlier have a flaw in the Low-level interface to RSA key pair generator, specifically RSA Key Pairs generated in low-level API with added certainty may have less M-R tests than expected. This appears to be fixed in versions BC 1.60 beta 4 and later, BC-FJA 1.0.2 and later.
<p>Publish Date: 2018-06-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000180>CVE-2018-1000180</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1000180">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1000180</a></p>
<p>Release Date: 2018-06-05</p>
<p>Fix Resolution: org.bouncycastle:bcprov-jdk15on:1.60,org.bouncycastle:bcprov-jdk14:1.60,org.bouncycastle:bcprov-ext-jdk14:1.60,org.bouncycastle:bcprov-ext-jdk15on:1.60</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-1000180 (High) detected in bcprov-jdk15on-1.56.jar - ## CVE-2018-1000180 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcprov-jdk15on-1.56.jar</b></p></summary>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptographic algorithms. This jar contains JCE provider and lightweight API for the Bouncy Castle Cryptography APIs for JDK 1.5 to JDK 1.8.</p>
<p>Library home page: <a href="http://www.bouncycastle.org/java.html">http://www.bouncycastle.org/java.html</a></p>
<p>Path to dependency file: Android-Common-Utils4/common4/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.bouncycastle/bcprov-jdk15on/1.56/a153c6f9744a3e9dd6feab5e210e1c9861362ec7/bcprov-jdk15on-1.56.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-27.1.2.jar (Root Library)
- sdk-common-27.1.2.jar
- :x: **bcprov-jdk15on-1.56.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Baneeishaque/Android-Common-Utils4/commit/e8328a1ad0239aaf16726916e083bb49de9642ec">e8328a1ad0239aaf16726916e083bb49de9642ec</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Bouncy Castle BC 1.54 - 1.59, BC-FJA 1.0.0, BC-FJA 1.0.1 and earlier have a flaw in the Low-level interface to RSA key pair generator, specifically RSA Key Pairs generated in low-level API with added certainty may have less M-R tests than expected. This appears to be fixed in versions BC 1.60 beta 4 and later, BC-FJA 1.0.2 and later.
<p>Publish Date: 2018-06-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000180>CVE-2018-1000180</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1000180">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1000180</a></p>
<p>Release Date: 2018-06-05</p>
<p>Fix Resolution: org.bouncycastle:bcprov-jdk15on:1.60,org.bouncycastle:bcprov-jdk14:1.60,org.bouncycastle:bcprov-ext-jdk14:1.60,org.bouncycastle:bcprov-ext-jdk15on:1.60</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_defect | cve high detected in bcprov jar cve high severity vulnerability vulnerable library bcprov jar the bouncy castle crypto package is a java implementation of cryptographic algorithms this jar contains jce provider and lightweight api for the bouncy castle cryptography apis for jdk to jdk library home page a href path to dependency file android common build gradle path to vulnerable library home wss scanner gradle caches modules files org bouncycastle bcprov bcprov jar dependency hierarchy lint gradle jar root library sdk common jar x bcprov jar vulnerable library found in head commit a href found in base branch master vulnerability details bouncy castle bc bc fja bc fja and earlier have a flaw in the low level interface to rsa key pair generator specifically rsa key pairs generated in low level api with added certainty may have less m r tests than expected this appears to be fixed in versions bc beta and later bc fja and later publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org bouncycastle bcprov org bouncycastle bcprov org bouncycastle bcprov ext org bouncycastle bcprov ext step up your open source security game with whitesource | 0 |
47,187 | 13,056,048,886 | IssuesEvent | 2020-07-30 03:30:01 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | closed | trac attach file to ticket fails. (Trac #108) | Migrated from Trac defect infrastructure | Trying to attach a .py script to a ticket from OS X on my MacBook.
It barfs.
Migrated from https://code.icecube.wisc.edu/ticket/108
```json
{
"status": "closed",
"changetime": "2007-12-03T15:32:37",
"description": "Trying to attach a .py script to a ticket from OS X on my MacBook.\n\nIt barfs.",
"reporter": "blaufuss",
"cc": "",
"resolution": "fixed",
"_ts": "1196695957000000",
"component": "infrastructure",
"summary": "trac attach file to ticket fails.",
"priority": "normal",
"keywords": "",
"time": "2007-08-31T18:54:13",
"milestone": "",
"owner": "cgils",
"type": "defect"
}
```
| 1.0 | trac attach file to ticket fails. (Trac #108) - Trying to attach a .py script to a ticket from OS X on my MacBook.
It barfs.
Migrated from https://code.icecube.wisc.edu/ticket/108
```json
{
"status": "closed",
"changetime": "2007-12-03T15:32:37",
"description": "Trying to attach a .py script to a ticket from OS X on my MacBook.\n\nIt barfs.",
"reporter": "blaufuss",
"cc": "",
"resolution": "fixed",
"_ts": "1196695957000000",
"component": "infrastructure",
"summary": "trac attach file to ticket fails.",
"priority": "normal",
"keywords": "",
"time": "2007-08-31T18:54:13",
"milestone": "",
"owner": "cgils",
"type": "defect"
}
```
| defect | trac attach file to ticket fails trac trying to attach a py script to a ticket from os x on my macbook it barfs migrated from json status closed changetime description trying to attach a py script to a ticket from os x on my macbook n nit barfs reporter blaufuss cc resolution fixed ts component infrastructure summary trac attach file to ticket fails priority normal keywords time milestone owner cgils type defect | 1 |
40,502 | 10,022,948,889 | IssuesEvent | 2019-07-16 17:58:12 | vector-im/riot-web | https://api.github.com/repos/vector-im/riot-web | closed | Create a new chat or reuse an existing one includes rooms you're no longer in | Community PR bug defect p1 | If you start a chat with someone then leave it and go to make another one you'll be prompted to re-use the previous one which you have no way of rejoining | 1.0 | Create a new chat or reuse an existing one includes rooms you're no longer in - If you start a chat with someone then leave it and go to make another one you'll be prompted to re-use the previous one which you have no way of rejoining | defect | create a new chat or reuse an existing one includes rooms you re no longer in if you start a chat with someone then leave it and go to make another one you ll be prompted to re use the previous one which you have no way of rejoining | 1 |
63,885 | 12,396,057,465 | IssuesEvent | 2020-05-20 19:48:40 | pnp/pnpjs | https://api.github.com/repos/pnp/pnpjs | closed | pnpjs and jest / enzyme tests | area: code status: answered type: question |
### Category
- [ ] Enhancement
- [ ] Bug
- [x ] Question
- [ ] Documentation gap/issue
### Version
Hello,
when I am reference pnpjs in my react typescript project, I am not able to run my tests anymore.
The Typescript does not get compiled. A thread about that can be found here:
https://github.com/pnp/pnpjs/issues/1058
My Question:
Is it a valid solution to use @pnp/common instead of pnpjs?
When I reference @pnp/common then my tests are running fine and the code also works.
What is the exact difference between pnpcommon and pnpjs? Is it just a subset of pnpjs functionalities or is it a copy of functionalities?
Thanks :-) | 1.0 | pnpjs and jest / enzyme tests -
### Category
- [ ] Enhancement
- [ ] Bug
- [x ] Question
- [ ] Documentation gap/issue
### Version
Hello,
when I am reference pnpjs in my react typescript project, I am not able to run my tests anymore.
The Typescript does not get compiled. A thread about that can be found here:
https://github.com/pnp/pnpjs/issues/1058
My Question:
Is it a valid solution to use @pnp/common instead of pnpjs?
When I reference @pnp/common then my tests are running fine and the code also works.
What is the exact difference between pnpcommon and pnpjs? Is it just a subset of pnpjs functionalities or is it a copy of functionalities?
Thanks :-) | non_defect | pnpjs and jest enzyme tests category enhancement bug question documentation gap issue version hello when i am reference pnpjs in my react typescript project i am not able to run my tests anymore the typescript does not get compiled a thread about that can be found here my question is it a valid solution to use pnp common instead of pnpjs when i reference pnp common then my tests are running fine and the code also works what is the exact difference between pnpcommon and pnpjs is it just a subset of pnpjs functionalities or is it a copy of functionalities thanks | 0 |
16,076 | 2,870,704,972 | IssuesEvent | 2015-06-07 12:43:49 | arescentral/antares | https://api.github.com/repos/arescentral/antares | opened | LoDPI cursor in HiDPI mode | Complexity:Low Data HiDPI Priority:Low Type:Defect | On HiDPI displays, the sprite cursor appears pixelated. This is an easy resource to design a HiDPI version of. We should do so and update src/game/cursor.cpp to use the right version. Also:
* We should probably move it into the data/ directory and distribute it with the application, instead of getting it from the factory scenario.
* Maybe it doesn't make any sense to keep it in a SMIV anymore either. | 1.0 | LoDPI cursor in HiDPI mode - On HiDPI displays, the sprite cursor appears pixelated. This is an easy resource to design a HiDPI version of. We should do so and update src/game/cursor.cpp to use the right version. Also:
* We should probably move it into the data/ directory and distribute it with the application, instead of getting it from the factory scenario.
* Maybe it doesn't make any sense to keep it in a SMIV anymore either. | defect | lodpi cursor in hidpi mode on hidpi displays the sprite cursor appears pixelated this is an easy resource to design a hidpi version of we should do so and update src game cursor cpp to use the right version also we should probably move it into the data directory and distribute it with the application instead of getting it from the factory scenario maybe it doesn t make any sense to keep it in a smiv anymore either | 1 |
27,307 | 4,958,870,180 | IssuesEvent | 2016-12-02 11:16:12 | rbei-etas/busmaster | https://api.github.com/repos/rbei-etas/busmaster | opened | Save configuration popup is shown even if no changes are made to the configuration | 1.3 patch (defect) 3.3 low priority (EC3) | 1. Open Busmaster application
2. Load an existing configuration
3. Click on file->Exit
A popup asking to save the changes to the configuration is displayed even though no changes are made.
| 1.0 | Save configuration popup is shown even if no changes are made to the configuration - 1. Open Busmaster application
2. Load an existing configuration
3. Click on file->Exit
A popup asking to save the changes to the configuration is displayed even though no changes are made.
| defect | save configuration popup is shown even if no changes are made to the configuration open busmaster application load an existing configuration click on file exit a popup asking to save the changes to the configuration is displayed even though no changes are made | 1 |
143,140 | 11,517,549,744 | IssuesEvent | 2020-02-14 08:38:39 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | roachtest: disk-stalled/log=false,data=false failed | C-test-failure O-roachtest O-robot branch-master release-blocker | [(roachtest).disk-stalled/log=false,data=false failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=1749385&tab=buildLog) on [master@e671a4ef97cbc6cf5d22f8f322fd45733d302094](https://github.com/cockroachdb/cockroach/commits/e671a4ef97cbc6cf5d22f8f322fd45733d302094):
```
The test failed on branch=master, cloud=gce:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/disk-stalled/log=false_data=false/run_1
disk_stall.go:60,disk_stall.go:39,test_runner.go:741: error with attached stack trace:
main.execCmd
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:406
main.runDiskStalledDetection
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/disk_stall.go:59
main.registerDiskStalledDetection.func1
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/disk_stall.go:39
main.(*testRunner).runTest.func2
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/test_runner.go:741
runtime.goexit
/usr/local/go/src/runtime/asm_amd64.s:1357
- error with embedded safe details: %s returned:
stderr:
%s
stdout:
%s
-- arg 1: <string>
-- arg 2: <string>
-- arg 3: <string>
- /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod install teamcity-1749385-1581667748-25-n1cpu4:1 charybdefs returned:
stderr:
stdout:
--:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:22 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:23 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:24 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:25 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:26 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:27 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:28 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:29 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:30 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:31 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:32 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:33 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:34 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:35 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:36 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:37 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:38 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:39 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:40 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:41 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:42 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:43 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:44 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:45 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:46 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:47 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:48 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:49 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:50 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:51 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:52 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:53 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:54 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:55 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:56 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:57 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:58 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:59 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:00 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:01 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:02 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:03 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:04 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:05 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:06 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:07 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:08 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:09 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:10 --:--:-- 0curl: (7) Failed to connect to www-eu.apache.org port 80: Connection timed out
gzip: stdin: unexpected end of file
tar: Child returned status 1
tar: Error is not recoverable: exiting now
Error: exit status 2:
- exit status 1
```
<details><summary>More</summary><p>
Artifacts: [/disk-stalled/log=false,data=false](https://teamcity.cockroachdb.com/viewLog.html?buildId=1749385&tab=artifacts#/disk-stalled/log=false,data=false)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Adisk-stalled%2Flog%3Dfalse%2Cdata%3Dfalse.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| 2.0 | roachtest: disk-stalled/log=false,data=false failed - [(roachtest).disk-stalled/log=false,data=false failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=1749385&tab=buildLog) on [master@e671a4ef97cbc6cf5d22f8f322fd45733d302094](https://github.com/cockroachdb/cockroach/commits/e671a4ef97cbc6cf5d22f8f322fd45733d302094):
```
The test failed on branch=master, cloud=gce:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/disk-stalled/log=false_data=false/run_1
disk_stall.go:60,disk_stall.go:39,test_runner.go:741: error with attached stack trace:
main.execCmd
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:406
main.runDiskStalledDetection
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/disk_stall.go:59
main.registerDiskStalledDetection.func1
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/disk_stall.go:39
main.(*testRunner).runTest.func2
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/test_runner.go:741
runtime.goexit
/usr/local/go/src/runtime/asm_amd64.s:1357
- error with embedded safe details: %s returned:
stderr:
%s
stdout:
%s
-- arg 1: <string>
-- arg 2: <string>
-- arg 3: <string>
- /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod install teamcity-1749385-1581667748-25-n1cpu4:1 charybdefs returned:
stderr:
stdout:
--:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:22 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:23 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:24 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:25 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:26 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:27 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:28 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:29 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:30 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:31 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:32 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:33 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:34 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:35 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:36 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:37 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:38 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:39 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:40 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:41 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:42 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:43 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:44 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:45 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:46 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:47 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:48 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:49 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:50 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:51 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:52 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:53 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:54 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:55 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:56 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:57 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:58 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:01:59 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:00 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:01 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:02 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:03 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:04 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:05 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:06 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:07 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:08 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:09 --:--:-- 0
0 0 0 0 0 0 0 0 --:--:-- 0:02:10 --:--:-- 0curl: (7) Failed to connect to www-eu.apache.org port 80: Connection timed out
gzip: stdin: unexpected end of file
tar: Child returned status 1
tar: Error is not recoverable: exiting now
Error: exit status 2:
- exit status 1
```
<details><summary>More</summary><p>
Artifacts: [/disk-stalled/log=false,data=false](https://teamcity.cockroachdb.com/viewLog.html?buildId=1749385&tab=artifacts#/disk-stalled/log=false,data=false)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Adisk-stalled%2Flog%3Dfalse%2Cdata%3Dfalse.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| non_defect | roachtest disk stalled log false data false failed on the test failed on branch master cloud gce test artifacts and logs in home agent work go src github com cockroachdb cockroach artifacts disk stalled log false data false run disk stall go disk stall go test runner go error with attached stack trace main execcmd home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go main rundiskstalleddetection home agent work go src github com cockroachdb cockroach pkg cmd roachtest disk stall go main registerdiskstalleddetection home agent work go src github com cockroachdb cockroach pkg cmd roachtest disk stall go main testrunner runtest home agent work go src github com cockroachdb cockroach pkg cmd roachtest test runner go runtime goexit usr local go src runtime asm s error with embedded safe details s returned stderr s stdout s arg arg arg home agent work go src github com cockroachdb cockroach bin roachprod install teamcity charybdefs returned stderr stdout failed to connect to www eu apache org port connection timed out gzip stdin unexpected end of file tar child returned status tar error is not recoverable exiting now error exit status exit status more artifacts powered by | 0 |
20,112 | 3,295,641,545 | IssuesEvent | 2015-11-01 04:33:51 | duyetdev/latex-lab | https://api.github.com/repos/duyetdev/latex-lab | closed | Online preview: Space between compiled pages | auto-migrated Priority-Medium Type-Defect | ```
What steps will reproduce the problem?
1. Compile a document with more than one page
What is the expected output? What do you see instead?
There is no space between compiled pages when using the online preview.
Perhaps includes some spacing would be great.
What version of the product are you using? On what operating system?
Firefox 3.6.3, Vista
Please provide any additional information below.
This is of course doesn't affect the exported PDF version.
```
Original issue reported on code.google.com by `ghassane...@gmail.com` on 13 Apr 2010 at 4:16 | 1.0 | Online preview: Space between compiled pages - ```
What steps will reproduce the problem?
1. Compile a document with more than one page
What is the expected output? What do you see instead?
There is no space between compiled pages when using the online preview.
Perhaps includes some spacing would be great.
What version of the product are you using? On what operating system?
Firefox 3.6.3, Vista
Please provide any additional information below.
This is of course doesn't affect the exported PDF version.
```
Original issue reported on code.google.com by `ghassane...@gmail.com` on 13 Apr 2010 at 4:16 | defect | online preview space between compiled pages what steps will reproduce the problem compile a document with more than one page what is the expected output what do you see instead there is no space between compiled pages when using the online preview perhaps includes some spacing would be great what version of the product are you using on what operating system firefox vista please provide any additional information below this is of course doesn t affect the exported pdf version original issue reported on code google com by ghassane gmail com on apr at | 1 |
22,948 | 3,727,389,689 | IssuesEvent | 2016-03-06 08:05:21 | godfather1103/mentohust | https://api.github.com/repos/godfather1103/mentohust | closed | 锐捷4.63认证不了 | auto-migrated Priority-Medium Type-Defect | ```
学校升级锐捷到4.63,替换/etc/mentohust下的两个文件后,认证��
�示非管理员指定版本,使用sudo mentohust -v4.63
-w,认证还是相同提示,等认证四到五次,提示用户已列入黑
名单。求高手解决!!!!!!!!!!!!!!!!!!��
�
```
Original issue reported on code.google.com by `fulin...@yahoo.cn` on 26 May 2012 at 9:37 | 1.0 | 锐捷4.63认证不了 - ```
学校升级锐捷到4.63,替换/etc/mentohust下的两个文件后,认证��
�示非管理员指定版本,使用sudo mentohust -v4.63
-w,认证还是相同提示,等认证四到五次,提示用户已列入黑
名单。求高手解决!!!!!!!!!!!!!!!!!!��
�
```
Original issue reported on code.google.com by `fulin...@yahoo.cn` on 26 May 2012 at 9:37 | defect | ,替换 etc mentohust下的两个文件后,认证�� �示非管理员指定版本,使用sudo mentohust w,认证还是相同提示,等认证四到五次,提示用户已列入黑 名单。求高手解决!!!!!!!!!!!!!!!!!!�� � original issue reported on code google com by fulin yahoo cn on may at | 1 |
129,782 | 5,103,426,910 | IssuesEvent | 2017-01-04 21:23:02 | lxde/lxqt | https://api.github.com/repos/lxde/lxqt | closed | Improve the quality of bugs and pull requests | high-priority idea/discussion | We should provide Bug/PR templates per repo - could be helpful to get the needed informations.
https://github.com/blog/2111-issue-and-pull-request-templates
https://help.github.com/articles/creating-an-issue-template-for-your-repository/
https://help.github.com/articles/creating-an-issue-template-for-your-repository/ | 1.0 | Improve the quality of bugs and pull requests - We should provide Bug/PR templates per repo - could be helpful to get the needed informations.
https://github.com/blog/2111-issue-and-pull-request-templates
https://help.github.com/articles/creating-an-issue-template-for-your-repository/
https://help.github.com/articles/creating-an-issue-template-for-your-repository/ | non_defect | improve the quality of bugs and pull requests we should provide bug pr templates per repo could be helpful to get the needed informations | 0 |
75,906 | 26,143,102,675 | IssuesEvent | 2022-12-29 21:58:48 | BOINC/boinc | https://api.github.com/repos/BOINC/boinc | closed | BOINC unable to connect client | C: Client - Daemon C: Manager P: Undetermined R: invalid T: Defect Validate | BOINC unable to connect client
BOINC unable to connect client, not running any tasks
**Steps To Reproduce**
1. Unable to connect to client
2. Unable to run any tasks
**Expected behavior**
Must be able to connect to internet and automatically run tasks on my computer
**Screenshots**
**System Information**
- OS: Windows 11
- BOINC Version: 7.20.2 (64 bit)+virtualBox
| 1.0 | BOINC unable to connect client - BOINC unable to connect client
BOINC unable to connect client, not running any tasks
**Steps To Reproduce**
1. Unable to connect to client
2. Unable to run any tasks
**Expected behavior**
Must be able to connect to internet and automatically run tasks on my computer
**Screenshots**
**System Information**
- OS: Windows 11
- BOINC Version: 7.20.2 (64 bit)+virtualBox
| defect | boinc unable to connect client boinc unable to connect client boinc unable to connect client not running any tasks steps to reproduce unable to connect to client unable to run any tasks expected behavior must be able to connect to internet and automatically run tasks on my computer screenshots system information os windows boinc version bit virtualbox | 1 |
47,831 | 13,066,262,380 | IssuesEvent | 2020-07-30 21:19:42 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | closed | fixmes in weighting (Trac #1237) | Migrated from Trac combo core defect | python/fluxes.py: FIXME: this predicts a flux that is a factor of ~2 larger than Hoerandel
python/weighting.py: # FIXME: more careful checking of the parameters
Migrated from https://code.icecube.wisc.edu/ticket/1237
```json
{
"status": "closed",
"changetime": "2019-02-13T14:11:57",
"description": "python/fluxes.py:\tFIXME: this predicts a flux that is a factor of ~2 larger than Hoerandel\npython/weighting.py:\t\t\t\t# FIXME: more careful checking of the parameters",
"reporter": "kjmeagher",
"cc": "",
"resolution": "fixed",
"_ts": "1550067117911749",
"component": "combo core",
"summary": "fixmes in weighting",
"priority": "normal",
"keywords": "",
"time": "2015-08-20T08:27:35",
"milestone": "",
"owner": "jvansanten",
"type": "defect"
}
```
| 1.0 | fixmes in weighting (Trac #1237) - python/fluxes.py: FIXME: this predicts a flux that is a factor of ~2 larger than Hoerandel
python/weighting.py: # FIXME: more careful checking of the parameters
Migrated from https://code.icecube.wisc.edu/ticket/1237
```json
{
"status": "closed",
"changetime": "2019-02-13T14:11:57",
"description": "python/fluxes.py:\tFIXME: this predicts a flux that is a factor of ~2 larger than Hoerandel\npython/weighting.py:\t\t\t\t# FIXME: more careful checking of the parameters",
"reporter": "kjmeagher",
"cc": "",
"resolution": "fixed",
"_ts": "1550067117911749",
"component": "combo core",
"summary": "fixmes in weighting",
"priority": "normal",
"keywords": "",
"time": "2015-08-20T08:27:35",
"milestone": "",
"owner": "jvansanten",
"type": "defect"
}
```
| defect | fixmes in weighting trac python fluxes py fixme this predicts a flux that is a factor of larger than hoerandel python weighting py fixme more careful checking of the parameters migrated from json status closed changetime description python fluxes py tfixme this predicts a flux that is a factor of larger than hoerandel npython weighting py t t t t fixme more careful checking of the parameters reporter kjmeagher cc resolution fixed ts component combo core summary fixmes in weighting priority normal keywords time milestone owner jvansanten type defect | 1 |
115 | 2,534,508,513 | IssuesEvent | 2015-01-25 01:34:34 | symfony/symfony-docs | https://api.github.com/repos/symfony/symfony-docs | closed | [Cookbook] Security: How to create a custom Authentication Provider | Security | Hi there,
I've used http://symfony.com/doc/current/cookbook/security/custom_authentication_provider.html to create an authentication provider for facebook and helped someone doing it for another 3rd party API. Both times I didn't get it working without making the authentication.listener abstract with security.authentication.listener.abstract as the parent and extending Symfony\Bundle\SecurityBundle\DependencyInjection\Security\Factory\AbstractFactory instead of implementing Symfony\Bundle\SecurityBundle\DependencyInjection\Security\Factory\SecurityFactoryInterface.
My question: Is the described way still the best way to do it or should the tutorial be updated?
What's your opinion @schmittjoh? | True | [Cookbook] Security: How to create a custom Authentication Provider - Hi there,
I've used http://symfony.com/doc/current/cookbook/security/custom_authentication_provider.html to create an authentication provider for facebook and helped someone doing it for another 3rd party API. Both times I didn't get it working without making the authentication.listener abstract with security.authentication.listener.abstract as the parent and extending Symfony\Bundle\SecurityBundle\DependencyInjection\Security\Factory\AbstractFactory instead of implementing Symfony\Bundle\SecurityBundle\DependencyInjection\Security\Factory\SecurityFactoryInterface.
My question: Is the described way still the best way to do it or should the tutorial be updated?
What's your opinion @schmittjoh? | non_defect | security how to create a custom authentication provider hi there i ve used to create an authentication provider for facebook and helped someone doing it for another party api both times i didn t get it working without making the authentication listener abstract with security authentication listener abstract as the parent and extending symfony bundle securitybundle dependencyinjection security factory abstractfactory instead of implementing symfony bundle securitybundle dependencyinjection security factory securityfactoryinterface my question is the described way still the best way to do it or should the tutorial be updated what s your opinion schmittjoh | 0 |
8,847 | 2,612,907,827 | IssuesEvent | 2015-02-27 17:26:28 | chrsmith/windows-package-manager | https://api.github.com/repos/chrsmith/windows-package-manager | closed | Error installing MP3TAG 2.52 | auto-migrated Milestone-End_Of_Month Type-Defect | ```
What steps will reproduce the problem?
1.Install MP3TAG 2.25
What is the expected output? What do you see instead?
App installed. I see an error: Error: Installing / Installing Mp3tag 2.52: Hash
sum (SHA1) 981dc8c03fc7aa7b8e075cc53fef03380c6eaeb1 found, but
8d4bc35d4a878cdde5c82a8d0fa0c974172ed91a was expected. The file has changed.
What version of the product are you using? On what operating system?
1.17.6 - Win 7 64Bit
Please provide any additional information below.
```
Original issue reported on code.google.com by `leonardo...@gmail.com` on 26 Oct 2012 at 10:27 | 1.0 | Error installing MP3TAG 2.52 - ```
What steps will reproduce the problem?
1.Install MP3TAG 2.25
What is the expected output? What do you see instead?
App installed. I see an error: Error: Installing / Installing Mp3tag 2.52: Hash
sum (SHA1) 981dc8c03fc7aa7b8e075cc53fef03380c6eaeb1 found, but
8d4bc35d4a878cdde5c82a8d0fa0c974172ed91a was expected. The file has changed.
What version of the product are you using? On what operating system?
1.17.6 - Win 7 64Bit
Please provide any additional information below.
```
Original issue reported on code.google.com by `leonardo...@gmail.com` on 26 Oct 2012 at 10:27 | defect | error installing what steps will reproduce the problem install what is the expected output what do you see instead app installed i see an error error installing installing hash sum found but was expected the file has changed what version of the product are you using on what operating system win please provide any additional information below original issue reported on code google com by leonardo gmail com on oct at | 1 |
51,932 | 13,211,340,539 | IssuesEvent | 2020-08-15 22:25:49 | icecube-trac/tix4 | https://api.github.com/repos/icecube-trac/tix4 | opened | closing new tickets doesn't generate email (Trac #1303) | Incomplete Migration Migrated from Trac defect infrastructure | <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/1303">https://code.icecube.wisc.edu/projects/icecube/ticket/1303</a>, reported by david.schultzand owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2015-08-31T21:29:08",
"_ts": "1441056548802590",
"description": "When I close a \"new\" ticket via a commit, it does not generate email or go to the slack bot.",
"reporter": "david.schultz",
"cc": "",
"resolution": "fixed",
"time": "2015-08-28T22:46:18",
"component": "infrastructure",
"summary": "closing new tickets doesn't generate email",
"priority": "major",
"keywords": "",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
| 1.0 | closing new tickets doesn't generate email (Trac #1303) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/1303">https://code.icecube.wisc.edu/projects/icecube/ticket/1303</a>, reported by david.schultzand owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2015-08-31T21:29:08",
"_ts": "1441056548802590",
"description": "When I close a \"new\" ticket via a commit, it does not generate email or go to the slack bot.",
"reporter": "david.schultz",
"cc": "",
"resolution": "fixed",
"time": "2015-08-28T22:46:18",
"component": "infrastructure",
"summary": "closing new tickets doesn't generate email",
"priority": "major",
"keywords": "",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
| defect | closing new tickets doesn t generate email trac migrated from json status closed changetime ts description when i close a new ticket via a commit it does not generate email or go to the slack bot reporter david schultz cc resolution fixed time component infrastructure summary closing new tickets doesn t generate email priority major keywords milestone owner nega type defect | 1 |
487,917 | 14,061,264,511 | IssuesEvent | 2020-11-03 07:50:03 | AY2021S1-CS2103T-T13-1/tp | https://api.github.com/repos/AY2021S1-CS2103T-T13-1/tp | closed | Remove tags from VirusTracker | Implementation priority.Medium | Tags is a legacy from addressbook and serves no purpose within VirusTracker. This aspect ought to be removed to make VirusTracker more specialised and to make each Person panel cleaner. | 1.0 | Remove tags from VirusTracker - Tags is a legacy from addressbook and serves no purpose within VirusTracker. This aspect ought to be removed to make VirusTracker more specialised and to make each Person panel cleaner. | non_defect | remove tags from virustracker tags is a legacy from addressbook and serves no purpose within virustracker this aspect ought to be removed to make virustracker more specialised and to make each person panel cleaner | 0 |
18,778 | 3,086,888,960 | IssuesEvent | 2015-08-25 07:58:43 | NamPNQ/html5slides | https://api.github.com/repos/NamPNQ/html5slides | closed | Does not work in Latest Chrome and Safari on Mac OS | auto-migrated Priority-Medium Type-Defect | ```
I was forwarded a presentation built with this tool.
In Chrome and Safari on my mac, it shows the first 3 slides.
Then I am unable to move pass the third slide.
This behavior is also repeatable with the sample slide show from this project
site as well.
However, it seems to work ok in Firefox on the mac.
Environment
Mac OS 10.7.3
Chrome 18.0.1025.168
Safari Version 5.1.3 (7534.53.10)
```
Original issue reported on code.google.com by `vladimir...@gmail.com` on 3 May 2012 at 12:06 | 1.0 | Does not work in Latest Chrome and Safari on Mac OS - ```
I was forwarded a presentation built with this tool.
In Chrome and Safari on my mac, it shows the first 3 slides.
Then I am unable to move pass the third slide.
This behavior is also repeatable with the sample slide show from this project
site as well.
However, it seems to work ok in Firefox on the mac.
Environment
Mac OS 10.7.3
Chrome 18.0.1025.168
Safari Version 5.1.3 (7534.53.10)
```
Original issue reported on code.google.com by `vladimir...@gmail.com` on 3 May 2012 at 12:06 | defect | does not work in latest chrome and safari on mac os i was forwarded a presentation built with this tool in chrome and safari on my mac it shows the first slides then i am unable to move pass the third slide this behavior is also repeatable with the sample slide show from this project site as well however it seems to work ok in firefox on the mac environment mac os chrome safari version original issue reported on code google com by vladimir gmail com on may at | 1 |
32,141 | 6,720,280,279 | IssuesEvent | 2017-10-16 07:05:29 | primefaces/primereact | https://api.github.com/repos/primefaces/primereact | closed | Growl doesn't call onClear method | defect | Hi,
Growl doesn't call the onClear method because the onClick eventhandler of the close button calls the remove function.
https://github.com/primefaces/primereact/blob/e37db7e7396cd1598590a55d91975af279448a6a/src/components/growl/Growl.js#L88
Seems that Messages does it right.
https://github.com/primefaces/primereact/blob/e37db7e7396cd1598590a55d91975af279448a6a/src/components/messages/Messages.js#L61
Is this a known issue? I can't find anything about it in the documentation or in the github issues. | 1.0 | Growl doesn't call onClear method - Hi,
Growl doesn't call the onClear method because the onClick eventhandler of the close button calls the remove function.
https://github.com/primefaces/primereact/blob/e37db7e7396cd1598590a55d91975af279448a6a/src/components/growl/Growl.js#L88
Seems that Messages does it right.
https://github.com/primefaces/primereact/blob/e37db7e7396cd1598590a55d91975af279448a6a/src/components/messages/Messages.js#L61
Is this a known issue? I can't find anything about it in the documentation or in the github issues. | defect | growl doesn t call onclear method hi growl doesn t call the onclear method because the onclick eventhandler of the close button calls the remove function seems that messages does it right is this a known issue i can t find anything about it in the documentation or in the github issues | 1 |
237,702 | 26,085,305,055 | IssuesEvent | 2022-12-26 01:29:50 | michaeldotson/outerspace-vue | https://api.github.com/repos/michaeldotson/outerspace-vue | opened | CVE-2022-46175 (High) detected in multiple libraries | security vulnerability | ## CVE-2022-46175 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>json5-2.1.0.tgz</b>, <b>json5-0.5.1.tgz</b>, <b>json5-1.0.1.tgz</b></p></summary>
<p>
<details><summary><b>json5-2.1.0.tgz</b></p></summary>
<p>JSON for humans.</p>
<p>Library home page: <a href="https://registry.npmjs.org/json5/-/json5-2.1.0.tgz">https://registry.npmjs.org/json5/-/json5-2.1.0.tgz</a></p>
<p>Path to dependency file: /outerspace-vue/package.json</p>
<p>Path to vulnerable library: /node_modules/json5/package.json</p>
<p>
Dependency Hierarchy:
- cli-plugin-babel-3.7.0.tgz (Root Library)
- core-7.4.4.tgz
- :x: **json5-2.1.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>json5-0.5.1.tgz</b></p></summary>
<p>JSON for the ES5 era.</p>
<p>Library home page: <a href="https://registry.npmjs.org/json5/-/json5-0.5.1.tgz">https://registry.npmjs.org/json5/-/json5-0.5.1.tgz</a></p>
<p>Path to dependency file: /outerspace-vue/package.json</p>
<p>Path to vulnerable library: /node_modules/html-webpack-plugin/node_modules/json5/package.json</p>
<p>
Dependency Hierarchy:
- cli-plugin-babel-3.7.0.tgz (Root Library)
- babel-preset-app-3.7.0.tgz
- babel-plugin-module-resolver-3.2.0.tgz
- find-babel-config-1.2.0.tgz
- :x: **json5-0.5.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>json5-1.0.1.tgz</b></p></summary>
<p>JSON for humans.</p>
<p>Library home page: <a href="https://registry.npmjs.org/json5/-/json5-1.0.1.tgz">https://registry.npmjs.org/json5/-/json5-1.0.1.tgz</a></p>
<p>Path to dependency file: /outerspace-vue/package.json</p>
<p>Path to vulnerable library: /node_modules/loader-utils/node_modules/json5/package.json</p>
<p>
Dependency Hierarchy:
- cli-plugin-babel-3.7.0.tgz (Root Library)
- babel-loader-8.0.5.tgz
- loader-utils-1.2.3.tgz
- :x: **json5-1.0.1.tgz** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
JSON5 is an extension to the popular JSON file format that aims to be easier to write and maintain by hand (e.g. for config files). The `parse` method of the JSON5 library before and including version `2.2.1` does not restrict parsing of keys named `__proto__`, allowing specially crafted strings to pollute the prototype of the resulting object. This vulnerability pollutes the prototype of the object returned by `JSON5.parse` and not the global Object prototype, which is the commonly understood definition of Prototype Pollution. However, polluting the prototype of a single object can have significant security impact for an application if the object is later used in trusted operations. This vulnerability could allow an attacker to set arbitrary and unexpected keys on the object returned from `JSON5.parse`. The actual impact will depend on how applications utilize the returned object and how they filter unwanted keys, but could include denial of service, cross-site scripting, elevation of privilege, and in extreme cases, remote code execution. `JSON5.parse` should restrict parsing of `__proto__` keys when parsing JSON strings to objects. As a point of reference, the `JSON.parse` method included in JavaScript ignores `__proto__` keys. Simply changing `JSON5.parse` to `JSON.parse` in the examples above mitigates this vulnerability. This vulnerability is patched in json5 version 2.2.2 and later.
<p>Publish Date: 2022-12-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-46175>CVE-2022-46175</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-46175">https://www.cve.org/CVERecord?id=CVE-2022-46175</a></p>
<p>Release Date: 2022-12-24</p>
<p>Fix Resolution: json5 - 2.2.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-46175 (High) detected in multiple libraries - ## CVE-2022-46175 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>json5-2.1.0.tgz</b>, <b>json5-0.5.1.tgz</b>, <b>json5-1.0.1.tgz</b></p></summary>
<p>
<details><summary><b>json5-2.1.0.tgz</b></p></summary>
<p>JSON for humans.</p>
<p>Library home page: <a href="https://registry.npmjs.org/json5/-/json5-2.1.0.tgz">https://registry.npmjs.org/json5/-/json5-2.1.0.tgz</a></p>
<p>Path to dependency file: /outerspace-vue/package.json</p>
<p>Path to vulnerable library: /node_modules/json5/package.json</p>
<p>
Dependency Hierarchy:
- cli-plugin-babel-3.7.0.tgz (Root Library)
- core-7.4.4.tgz
- :x: **json5-2.1.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>json5-0.5.1.tgz</b></p></summary>
<p>JSON for the ES5 era.</p>
<p>Library home page: <a href="https://registry.npmjs.org/json5/-/json5-0.5.1.tgz">https://registry.npmjs.org/json5/-/json5-0.5.1.tgz</a></p>
<p>Path to dependency file: /outerspace-vue/package.json</p>
<p>Path to vulnerable library: /node_modules/html-webpack-plugin/node_modules/json5/package.json</p>
<p>
Dependency Hierarchy:
- cli-plugin-babel-3.7.0.tgz (Root Library)
- babel-preset-app-3.7.0.tgz
- babel-plugin-module-resolver-3.2.0.tgz
- find-babel-config-1.2.0.tgz
- :x: **json5-0.5.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>json5-1.0.1.tgz</b></p></summary>
<p>JSON for humans.</p>
<p>Library home page: <a href="https://registry.npmjs.org/json5/-/json5-1.0.1.tgz">https://registry.npmjs.org/json5/-/json5-1.0.1.tgz</a></p>
<p>Path to dependency file: /outerspace-vue/package.json</p>
<p>Path to vulnerable library: /node_modules/loader-utils/node_modules/json5/package.json</p>
<p>
Dependency Hierarchy:
- cli-plugin-babel-3.7.0.tgz (Root Library)
- babel-loader-8.0.5.tgz
- loader-utils-1.2.3.tgz
- :x: **json5-1.0.1.tgz** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
JSON5 is an extension to the popular JSON file format that aims to be easier to write and maintain by hand (e.g. for config files). The `parse` method of the JSON5 library before and including version `2.2.1` does not restrict parsing of keys named `__proto__`, allowing specially crafted strings to pollute the prototype of the resulting object. This vulnerability pollutes the prototype of the object returned by `JSON5.parse` and not the global Object prototype, which is the commonly understood definition of Prototype Pollution. However, polluting the prototype of a single object can have significant security impact for an application if the object is later used in trusted operations. This vulnerability could allow an attacker to set arbitrary and unexpected keys on the object returned from `JSON5.parse`. The actual impact will depend on how applications utilize the returned object and how they filter unwanted keys, but could include denial of service, cross-site scripting, elevation of privilege, and in extreme cases, remote code execution. `JSON5.parse` should restrict parsing of `__proto__` keys when parsing JSON strings to objects. As a point of reference, the `JSON.parse` method included in JavaScript ignores `__proto__` keys. Simply changing `JSON5.parse` to `JSON.parse` in the examples above mitigates this vulnerability. This vulnerability is patched in json5 version 2.2.2 and later.
<p>Publish Date: 2022-12-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-46175>CVE-2022-46175</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-46175">https://www.cve.org/CVERecord?id=CVE-2022-46175</a></p>
<p>Release Date: 2022-12-24</p>
<p>Fix Resolution: json5 - 2.2.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_defect | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries tgz tgz tgz tgz json for humans library home page a href path to dependency file outerspace vue package json path to vulnerable library node modules package json dependency hierarchy cli plugin babel tgz root library core tgz x tgz vulnerable library tgz json for the era library home page a href path to dependency file outerspace vue package json path to vulnerable library node modules html webpack plugin node modules package json dependency hierarchy cli plugin babel tgz root library babel preset app tgz babel plugin module resolver tgz find babel config tgz x tgz vulnerable library tgz json for humans library home page a href path to dependency file outerspace vue package json path to vulnerable library node modules loader utils node modules package json dependency hierarchy cli plugin babel tgz root library babel loader tgz loader utils tgz x tgz vulnerable library vulnerability details is an extension to the popular json file format that aims to be easier to write and maintain by hand e g for config files the parse method of the library before and including version does not restrict parsing of keys named proto allowing specially crafted strings to pollute the prototype of the resulting object this vulnerability pollutes the prototype of the object returned by parse and not the global object prototype which is the commonly understood definition of prototype pollution however polluting the prototype of a single object can have significant security impact for an application if the object is later used in trusted operations this vulnerability could allow an attacker to set arbitrary and unexpected keys on the object returned from parse the actual impact will depend on how applications utilize the returned object and how they filter unwanted keys but could include denial of service cross site scripting elevation of privilege and in extreme cases remote code execution parse should restrict parsing of proto keys when parsing json strings to objects as a point of reference the json parse method included in javascript ignores proto keys simply changing parse to json parse in the examples above mitigates this vulnerability this vulnerability is patched in version and later publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact low availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
65,451 | 19,523,708,496 | IssuesEvent | 2021-12-30 01:10:24 | scipy/scipy | https://api.github.com/repos/scipy/scipy | closed | BUG: owens_t(h, infinity) is not correct | defect scipy.special | ### Describe your issue.
Hello,
`owens_t(0, inf)` gives `0.5`. However `owens_t(a, inf)` is `atan(a)/(2*pi)` , so `owens_t(0, inf)` shoud give `0.25`.
### Reproducing Code Example
```python
from scipy import special
from math import atan, pi, inf
special.owens_t(0,inf)
# 0.5
atan(inf)/2/pi
# 0.25
```
### Error message
```shell
No error message
```
### SciPy/NumPy/Python version information
scipy 1.7.1, python 3.9.5 | 1.0 | BUG: owens_t(h, infinity) is not correct - ### Describe your issue.
Hello,
`owens_t(0, inf)` gives `0.5`. However `owens_t(a, inf)` is `atan(a)/(2*pi)` , so `owens_t(0, inf)` shoud give `0.25`.
### Reproducing Code Example
```python
from scipy import special
from math import atan, pi, inf
special.owens_t(0,inf)
# 0.5
atan(inf)/2/pi
# 0.25
```
### Error message
```shell
No error message
```
### SciPy/NumPy/Python version information
scipy 1.7.1, python 3.9.5 | defect | bug owens t h infinity is not correct describe your issue hello owens t inf gives however owens t a inf is atan a pi so owens t inf shoud give reproducing code example python from scipy import special from math import atan pi inf special owens t inf atan inf pi error message shell no error message scipy numpy python version information scipy python | 1 |
74,310 | 25,049,695,043 | IssuesEvent | 2022-11-05 18:23:46 | scipy/scipy | https://api.github.com/repos/scipy/scipy | opened | CircleCI is failing to run for recent pull requests. | defect CI | CircleCI is failing in recent pull requests. The important error message appears to be
```
ERROR: Could not detect Ninja v1.8.2 or newer
```
<details>
<summary>The full CircleCI log from a recent PR (103 lines).</summary>
```
💻 meson setup /home/circleci/repo/build --prefix
/home/circleci/repo/build-install
The Meson build system
Version: 0.63.3
Source dir: /home/circleci/repo
Build dir: /home/circleci/repo/build
Build type: native build
Project name: SciPy
Project version: 1.10.0.dev0
C compiler for the host machine: ccache cc (gcc 11.3.0 "cc (Ubuntu 11.3.0-1ubuntu1~22.04) 11.3.0")
C linker for the host machine: cc ld.bfd 2.38
C++ compiler for the host machine: ccache c++ (gcc 11.3.0 "c++ (Ubuntu 11.3.0-1ubuntu1~22.04) 11.3.0")
C++ linker for the host machine: c++ ld.bfd 2.38
Host machine cpu family: x86_64
Host machine cpu: x86_64
Compiler for C supports arguments -Wno-unused-but-set-variable: YES
Compiler for C supports arguments -Wno-unused-function: YES
Compiler for C supports arguments -Wno-conversion: YES
Compiler for C supports arguments -Wno-misleading-indentation: YES
Compiler for C supports arguments -Wno-incompatible-pointer-types: YES
Library m found: YES
Fortran compiler for the host machine: gfortran (gcc 11.3.0 "GNU Fortran (Ubuntu 11.3.0-1ubuntu1~22.04) 11.3.0")
Fortran linker for the host machine: gfortran ld.bfd 2.38
Compiler for Fortran supports arguments -Wno-conversion: YES
Checking if "-Wl,--version-script" : links: YES
Program cython found: YES (/home/circleci/.pyenv/versions/3.8.15/bin/cython)
Program pythran found: YES (/home/circleci/.pyenv/versions/3.8.15/bin/pythran)
Program cp found: YES (/usr/bin/cp)
Program python3 found: YES (/home/circleci/.pyenv/versions/3.8.15/bin/python3.8)
Found pkg-config: /usr/bin/pkg-config (0.29.2)
Run-time dependency threads found: YES
Library npymath found: YES
Library npyrandom found: YES
Run-time dependency openblas found: YES 0.3.20
Dependency openblas found: YES 0.3.20 (cached)
Program _build_utils/cythoner.py found: YES (/home/circleci/.pyenv/versions/3.8.15/bin/python3.8 /home/circleci/repo/scipy/_build_utils/cythoner.py)
Compiler for C supports arguments -Wno-maybe-uninitialized: YES
Compiler for C supports arguments -Wno-discarded-qualifiers: YES
Compiler for C supports arguments -Wno-empty-body: YES
Compiler for C supports arguments -Wno-implicit-function-declaration: YES
Compiler for C supports arguments -Wno-parentheses: YES
Compiler for C supports arguments -Wno-switch: YES
Compiler for C supports arguments -Wno-unused-label: YES
Compiler for C supports arguments -Wno-unused-variable: YES
Compiler for C++ supports arguments -Wno-cpp: YES
Compiler for C++ supports arguments -Wno-deprecated-declarations: YES
Compiler for C++ supports arguments -Wno-class-memaccess: YES
Compiler for C++ supports arguments -Wno-format-truncation: YES
Compiler for C++ supports arguments -Wno-non-virtual-dtor: YES
Compiler for C++ supports arguments -Wno-sign-compare: YES
Compiler for C++ supports arguments -Wno-switch: YES
Compiler for C++ supports arguments -Wno-terminate: YES
Compiler for C++ supports arguments -Wno-unused-but-set-variable: YES
Compiler for C++ supports arguments -Wno-unused-function: YES
Compiler for C++ supports arguments -Wno-unused-local-typedefs: YES
Compiler for C++ supports arguments -Wno-unused-variable: YES
Compiler for C++ supports arguments -Wno-int-in-bool-context: YES
Compiler for Fortran supports arguments -Wno-argument-mismatch: YES
Compiler for Fortran supports arguments -Wno-conversion: YES (cached)
Compiler for Fortran supports arguments -Wno-intrinsic-shadow: YES
Compiler for Fortran supports arguments -Wno-maybe-uninitialized: YES
Compiler for Fortran supports arguments -Wno-surprising: YES
Compiler for Fortran supports arguments -Wno-uninitialized: YES
Compiler for Fortran supports arguments -Wno-unused-dummy-argument: YES
Compiler for Fortran supports arguments -Wno-unused-label: YES
Compiler for Fortran supports arguments -Wno-unused-variable: YES
Compiler for Fortran supports arguments -Wno-tabs: YES
Compiler for Fortran supports arguments -Wno-argument-mismatch: YES (cached)
Compiler for Fortran supports arguments -Wno-conversion: YES (cached)
Compiler for Fortran supports arguments -Wno-maybe-uninitialized: YES (cached)
Compiler for Fortran supports arguments -Wno-unused-dummy-argument: YES (cached)
Compiler for Fortran supports arguments -Wno-unused-label: YES (cached)
Compiler for Fortran supports arguments -Wno-unused-variable: YES (cached)
Compiler for Fortran supports arguments -Wno-tabs: YES (cached)
Checking for function "open_memstream" : NO
Configuring messagestream_config.h using configuration
Compiler for Fortran supports arguments -w: YES
Checking for size of "void*" : 8
Compiler for C supports arguments -Wno-unused-variable: YES (cached)
Compiler for C supports arguments -Wno-parentheses: YES (cached)
Compiler for C supports arguments -Wno-unused-label: YES (cached)
Compiler for C supports arguments -Wno-implicit-function-declaration: YES (cached)
Compiler for C supports arguments -Wno-switch: YES (cached)
Compiler for Fortran supports arguments -w: YES (cached)
Checking for size of "void*" : 8
Build targets in project: 206
SciPy 1.10.0.dev0
User defined options
prefix: /home/circleci/repo/build-install
ERROR: Could not detect Ninja v1.8.2 or newer
A full log can be found at /home/circleci/repo/build/meson-logs/meson-log.txt
Meson build setup failed!
Exited with code exit status 1
``` | 1.0 | CircleCI is failing to run for recent pull requests. - CircleCI is failing in recent pull requests. The important error message appears to be
```
ERROR: Could not detect Ninja v1.8.2 or newer
```
<details>
<summary>The full CircleCI log from a recent PR (103 lines).</summary>
```
💻 meson setup /home/circleci/repo/build --prefix
/home/circleci/repo/build-install
The Meson build system
Version: 0.63.3
Source dir: /home/circleci/repo
Build dir: /home/circleci/repo/build
Build type: native build
Project name: SciPy
Project version: 1.10.0.dev0
C compiler for the host machine: ccache cc (gcc 11.3.0 "cc (Ubuntu 11.3.0-1ubuntu1~22.04) 11.3.0")
C linker for the host machine: cc ld.bfd 2.38
C++ compiler for the host machine: ccache c++ (gcc 11.3.0 "c++ (Ubuntu 11.3.0-1ubuntu1~22.04) 11.3.0")
C++ linker for the host machine: c++ ld.bfd 2.38
Host machine cpu family: x86_64
Host machine cpu: x86_64
Compiler for C supports arguments -Wno-unused-but-set-variable: YES
Compiler for C supports arguments -Wno-unused-function: YES
Compiler for C supports arguments -Wno-conversion: YES
Compiler for C supports arguments -Wno-misleading-indentation: YES
Compiler for C supports arguments -Wno-incompatible-pointer-types: YES
Library m found: YES
Fortran compiler for the host machine: gfortran (gcc 11.3.0 "GNU Fortran (Ubuntu 11.3.0-1ubuntu1~22.04) 11.3.0")
Fortran linker for the host machine: gfortran ld.bfd 2.38
Compiler for Fortran supports arguments -Wno-conversion: YES
Checking if "-Wl,--version-script" : links: YES
Program cython found: YES (/home/circleci/.pyenv/versions/3.8.15/bin/cython)
Program pythran found: YES (/home/circleci/.pyenv/versions/3.8.15/bin/pythran)
Program cp found: YES (/usr/bin/cp)
Program python3 found: YES (/home/circleci/.pyenv/versions/3.8.15/bin/python3.8)
Found pkg-config: /usr/bin/pkg-config (0.29.2)
Run-time dependency threads found: YES
Library npymath found: YES
Library npyrandom found: YES
Run-time dependency openblas found: YES 0.3.20
Dependency openblas found: YES 0.3.20 (cached)
Program _build_utils/cythoner.py found: YES (/home/circleci/.pyenv/versions/3.8.15/bin/python3.8 /home/circleci/repo/scipy/_build_utils/cythoner.py)
Compiler for C supports arguments -Wno-maybe-uninitialized: YES
Compiler for C supports arguments -Wno-discarded-qualifiers: YES
Compiler for C supports arguments -Wno-empty-body: YES
Compiler for C supports arguments -Wno-implicit-function-declaration: YES
Compiler for C supports arguments -Wno-parentheses: YES
Compiler for C supports arguments -Wno-switch: YES
Compiler for C supports arguments -Wno-unused-label: YES
Compiler for C supports arguments -Wno-unused-variable: YES
Compiler for C++ supports arguments -Wno-cpp: YES
Compiler for C++ supports arguments -Wno-deprecated-declarations: YES
Compiler for C++ supports arguments -Wno-class-memaccess: YES
Compiler for C++ supports arguments -Wno-format-truncation: YES
Compiler for C++ supports arguments -Wno-non-virtual-dtor: YES
Compiler for C++ supports arguments -Wno-sign-compare: YES
Compiler for C++ supports arguments -Wno-switch: YES
Compiler for C++ supports arguments -Wno-terminate: YES
Compiler for C++ supports arguments -Wno-unused-but-set-variable: YES
Compiler for C++ supports arguments -Wno-unused-function: YES
Compiler for C++ supports arguments -Wno-unused-local-typedefs: YES
Compiler for C++ supports arguments -Wno-unused-variable: YES
Compiler for C++ supports arguments -Wno-int-in-bool-context: YES
Compiler for Fortran supports arguments -Wno-argument-mismatch: YES
Compiler for Fortran supports arguments -Wno-conversion: YES (cached)
Compiler for Fortran supports arguments -Wno-intrinsic-shadow: YES
Compiler for Fortran supports arguments -Wno-maybe-uninitialized: YES
Compiler for Fortran supports arguments -Wno-surprising: YES
Compiler for Fortran supports arguments -Wno-uninitialized: YES
Compiler for Fortran supports arguments -Wno-unused-dummy-argument: YES
Compiler for Fortran supports arguments -Wno-unused-label: YES
Compiler for Fortran supports arguments -Wno-unused-variable: YES
Compiler for Fortran supports arguments -Wno-tabs: YES
Compiler for Fortran supports arguments -Wno-argument-mismatch: YES (cached)
Compiler for Fortran supports arguments -Wno-conversion: YES (cached)
Compiler for Fortran supports arguments -Wno-maybe-uninitialized: YES (cached)
Compiler for Fortran supports arguments -Wno-unused-dummy-argument: YES (cached)
Compiler for Fortran supports arguments -Wno-unused-label: YES (cached)
Compiler for Fortran supports arguments -Wno-unused-variable: YES (cached)
Compiler for Fortran supports arguments -Wno-tabs: YES (cached)
Checking for function "open_memstream" : NO
Configuring messagestream_config.h using configuration
Compiler for Fortran supports arguments -w: YES
Checking for size of "void*" : 8
Compiler for C supports arguments -Wno-unused-variable: YES (cached)
Compiler for C supports arguments -Wno-parentheses: YES (cached)
Compiler for C supports arguments -Wno-unused-label: YES (cached)
Compiler for C supports arguments -Wno-implicit-function-declaration: YES (cached)
Compiler for C supports arguments -Wno-switch: YES (cached)
Compiler for Fortran supports arguments -w: YES (cached)
Checking for size of "void*" : 8
Build targets in project: 206
SciPy 1.10.0.dev0
User defined options
prefix: /home/circleci/repo/build-install
ERROR: Could not detect Ninja v1.8.2 or newer
A full log can be found at /home/circleci/repo/build/meson-logs/meson-log.txt
Meson build setup failed!
Exited with code exit status 1
``` | defect | circleci is failing to run for recent pull requests circleci is failing in recent pull requests the important error message appears to be error could not detect ninja or newer the full circleci log from a recent pr lines 💻 meson setup home circleci repo build prefix home circleci repo build install the meson build system version source dir home circleci repo build dir home circleci repo build build type native build project name scipy project version c compiler for the host machine ccache cc gcc cc ubuntu c linker for the host machine cc ld bfd c compiler for the host machine ccache c gcc c ubuntu c linker for the host machine c ld bfd host machine cpu family host machine cpu compiler for c supports arguments wno unused but set variable yes compiler for c supports arguments wno unused function yes compiler for c supports arguments wno conversion yes compiler for c supports arguments wno misleading indentation yes compiler for c supports arguments wno incompatible pointer types yes library m found yes fortran compiler for the host machine gfortran gcc gnu fortran ubuntu fortran linker for the host machine gfortran ld bfd compiler for fortran supports arguments wno conversion yes checking if wl version script links yes program cython found yes home circleci pyenv versions bin cython program pythran found yes home circleci pyenv versions bin pythran program cp found yes usr bin cp program found yes home circleci pyenv versions bin found pkg config usr bin pkg config run time dependency threads found yes library npymath found yes library npyrandom found yes run time dependency openblas found yes dependency openblas found yes cached program build utils cythoner py found yes home circleci pyenv versions bin home circleci repo scipy build utils cythoner py compiler for c supports arguments wno maybe uninitialized yes compiler for c supports arguments wno discarded qualifiers yes compiler for c supports arguments wno empty body yes compiler for c supports arguments wno implicit function declaration yes compiler for c supports arguments wno parentheses yes compiler for c supports arguments wno switch yes compiler for c supports arguments wno unused label yes compiler for c supports arguments wno unused variable yes compiler for c supports arguments wno cpp yes compiler for c supports arguments wno deprecated declarations yes compiler for c supports arguments wno class memaccess yes compiler for c supports arguments wno format truncation yes compiler for c supports arguments wno non virtual dtor yes compiler for c supports arguments wno sign compare yes compiler for c supports arguments wno switch yes compiler for c supports arguments wno terminate yes compiler for c supports arguments wno unused but set variable yes compiler for c supports arguments wno unused function yes compiler for c supports arguments wno unused local typedefs yes compiler for c supports arguments wno unused variable yes compiler for c supports arguments wno int in bool context yes compiler for fortran supports arguments wno argument mismatch yes compiler for fortran supports arguments wno conversion yes cached compiler for fortran supports arguments wno intrinsic shadow yes compiler for fortran supports arguments wno maybe uninitialized yes compiler for fortran supports arguments wno surprising yes compiler for fortran supports arguments wno uninitialized yes compiler for fortran supports arguments wno unused dummy argument yes compiler for fortran supports arguments wno unused label yes compiler for fortran supports arguments wno unused variable yes compiler for fortran supports arguments wno tabs yes compiler for fortran supports arguments wno argument mismatch yes cached compiler for fortran supports arguments wno conversion yes cached compiler for fortran supports arguments wno maybe uninitialized yes cached compiler for fortran supports arguments wno unused dummy argument yes cached compiler for fortran supports arguments wno unused label yes cached compiler for fortran supports arguments wno unused variable yes cached compiler for fortran supports arguments wno tabs yes cached checking for function open memstream no configuring messagestream config h using configuration compiler for fortran supports arguments w yes checking for size of void compiler for c supports arguments wno unused variable yes cached compiler for c supports arguments wno parentheses yes cached compiler for c supports arguments wno unused label yes cached compiler for c supports arguments wno implicit function declaration yes cached compiler for c supports arguments wno switch yes cached compiler for fortran supports arguments w yes cached checking for size of void build targets in project scipy user defined options prefix home circleci repo build install error could not detect ninja or newer a full log can be found at home circleci repo build meson logs meson log txt meson build setup failed exited with code exit status | 1 |
247,515 | 7,919,426,361 | IssuesEvent | 2018-07-04 16:46:56 | Xceptance/neodymium-library | https://api.github.com/repos/Xceptance/neodymium-library | closed | Move test resources | Low Priority doneInDevelop recheckedInDevelop | Move test resources to the resources folder in test to reestablish the default behavior. | 1.0 | Move test resources - Move test resources to the resources folder in test to reestablish the default behavior. | non_defect | move test resources move test resources to the resources folder in test to reestablish the default behavior | 0 |
240,527 | 7,802,731,828 | IssuesEvent | 2018-06-10 15:47:58 | mapbox/mapboxgl-powerbi | https://api.github.com/repos/mapbox/mapboxgl-powerbi | closed | Add `rectangle` and `lasso` map filter selections | Priority: High feature request | # Feature request
This is a feature request built on top of the [data selection filter issue](https://github.com/mapbox/mapboxgl-powerbi/issues/2). A user should be able to select features in the map with both a `click` for a single feature, a rectangular `box`, or a free-form `lasso` select. This issue tracks work on the `lasso` select feature.
# Proof of concept
https://www.mapbox.com/analysis-demos/trees/
# Implementation
Adding lasso select should involve:
1. Adding an HTML select component to the map container. The select component should show a `rectangle` and a `lasso` icon. Selecting the `rectangle` button will put the map in rectangle feature select mode. Selecting the `lasso` will put the map in free-form select mode.
2. After entering select mode for `lasso`, when the user clicks on the map, the map will show an HTML polygon element that follows the users mouse cursor. When the user clicks a second time, the polygon the user drew will close, and map will exit select mode.
3. Given the drawn polygon, the Mapobx Visual will select all features that are contained by or intersect the drawn rectangle or lasso polygon.
cc/ @mtirwin @szilardhuber @endre-jenei @baspeti | 1.0 | Add `rectangle` and `lasso` map filter selections - # Feature request
This is a feature request built on top of the [data selection filter issue](https://github.com/mapbox/mapboxgl-powerbi/issues/2). A user should be able to select features in the map with both a `click` for a single feature, a rectangular `box`, or a free-form `lasso` select. This issue tracks work on the `lasso` select feature.
# Proof of concept
https://www.mapbox.com/analysis-demos/trees/
# Implementation
Adding lasso select should involve:
1. Adding an HTML select component to the map container. The select component should show a `rectangle` and a `lasso` icon. Selecting the `rectangle` button will put the map in rectangle feature select mode. Selecting the `lasso` will put the map in free-form select mode.
2. After entering select mode for `lasso`, when the user clicks on the map, the map will show an HTML polygon element that follows the users mouse cursor. When the user clicks a second time, the polygon the user drew will close, and map will exit select mode.
3. Given the drawn polygon, the Mapobx Visual will select all features that are contained by or intersect the drawn rectangle or lasso polygon.
cc/ @mtirwin @szilardhuber @endre-jenei @baspeti | non_defect | add rectangle and lasso map filter selections feature request this is a feature request built on top of the a user should be able to select features in the map with both a click for a single feature a rectangular box or a free form lasso select this issue tracks work on the lasso select feature proof of concept implementation adding lasso select should involve adding an html select component to the map container the select component should show a rectangle and a lasso icon selecting the rectangle button will put the map in rectangle feature select mode selecting the lasso will put the map in free form select mode after entering select mode for lasso when the user clicks on the map the map will show an html polygon element that follows the users mouse cursor when the user clicks a second time the polygon the user drew will close and map will exit select mode given the drawn polygon the mapobx visual will select all features that are contained by or intersect the drawn rectangle or lasso polygon cc mtirwin szilardhuber endre jenei baspeti | 0 |
58,480 | 16,551,386,934 | IssuesEvent | 2021-05-28 08:59:13 | jOOQ/jOOQ | https://api.github.com/repos/jOOQ/jOOQ | closed | Incorrect SQL generated for multi table DELETE with JOIN in MySQL | C: Functionality E: All Editions P: Medium R: Fixed T: Defect | MySQL supports multi table `DELETE` statements using joins or table lists, see https://github.com/jOOQ/jOOQ/issues/5230.
There are various syntaxes as can be seen in the documentation:
https://dev.mysql.com/doc/refman/8.0/en/delete.html
E.g.
```sql
DELETE t1, t2 FROM t1 INNER JOIN t2 INNER JOIN t3
WHERE t1.id=t2.id AND t2.id=t3.id;
```
While multi table `DELETE` might be supported separately using #5230, this issue here should fix the `JOIN` syntax for single table `DELETE` statements, which currently doesn't work. The semantics is that of the multi table delete. If single table deletes are preferred, `DELETE .. USING` should be used, instead #11925
----
See also:
- Convenience syntax: https://github.com/jOOQ/jOOQ/issues/3266
- Multi table delete support: https://github.com/jOOQ/jOOQ/issues/5230
| 1.0 | Incorrect SQL generated for multi table DELETE with JOIN in MySQL - MySQL supports multi table `DELETE` statements using joins or table lists, see https://github.com/jOOQ/jOOQ/issues/5230.
There are various syntaxes as can be seen in the documentation:
https://dev.mysql.com/doc/refman/8.0/en/delete.html
E.g.
```sql
DELETE t1, t2 FROM t1 INNER JOIN t2 INNER JOIN t3
WHERE t1.id=t2.id AND t2.id=t3.id;
```
While multi table `DELETE` might be supported separately using #5230, this issue here should fix the `JOIN` syntax for single table `DELETE` statements, which currently doesn't work. The semantics is that of the multi table delete. If single table deletes are preferred, `DELETE .. USING` should be used, instead #11925
----
See also:
- Convenience syntax: https://github.com/jOOQ/jOOQ/issues/3266
- Multi table delete support: https://github.com/jOOQ/jOOQ/issues/5230
| defect | incorrect sql generated for multi table delete with join in mysql mysql supports multi table delete statements using joins or table lists see there are various syntaxes as can be seen in the documentation e g sql delete from inner join inner join where id id and id id while multi table delete might be supported separately using this issue here should fix the join syntax for single table delete statements which currently doesn t work the semantics is that of the multi table delete if single table deletes are preferred delete using should be used instead see also convenience syntax multi table delete support | 1 |
2,669 | 9,166,415,362 | IssuesEvent | 2019-03-02 03:03:51 | Homebrew/homebrew-cask | https://api.github.com/repos/Homebrew/homebrew-cask | closed | Delete Homebrew/homebrew-cask-eid | awaiting maintainer feedback discussion | https://github.com/Homebrew/homebrew-cask-eid was well-intentioned, but it might be best if we delete it. It has few casks, they get few updates, when they do many times it requires more than a simple bump, and analytics shows too few downloads (the most popular one had 25 downloads in the last 90 days, and more than half had less than 7).
Leaving this open for a bit for disagreements. | True | Delete Homebrew/homebrew-cask-eid - https://github.com/Homebrew/homebrew-cask-eid was well-intentioned, but it might be best if we delete it. It has few casks, they get few updates, when they do many times it requires more than a simple bump, and analytics shows too few downloads (the most popular one had 25 downloads in the last 90 days, and more than half had less than 7).
Leaving this open for a bit for disagreements. | non_defect | delete homebrew homebrew cask eid was well intentioned but it might be best if we delete it it has few casks they get few updates when they do many times it requires more than a simple bump and analytics shows too few downloads the most popular one had downloads in the last days and more than half had less than leaving this open for a bit for disagreements | 0 |
50,929 | 13,187,981,061 | IssuesEvent | 2020-08-13 05:12:30 | icecube-trac/tix3 | https://api.github.com/repos/icecube-trac/tix3 | closed | trigger-sim broken for frame objects that are not in simclasses or dataclasses (Trac #1695) | Migrated from Trac combo simulation defect | trigger-sim broken for frame objects that are not in simclasses or dataclasses. Found this because trunk trigger-sim does not work for GENIE simulation. GENIE puts the `I3GENIEResultsDict` in the frame. When trigger-sim loops through the frame objects to find the `I3TriggerHierarchy`, python will hit the `I3GENIEResultsDict` in the frame and will throw an `Unregistred Class` error because the `I3GENIEResultsDict` is not part of dataclasses or simclasses.
It is a bad idea to assume that everything in a frame is deserializable. The correct solution is to pass a list of `I3TriggerHierarchy`s and have a default that covers the standard use case.
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1695">https://code.icecube.wisc.edu/ticket/1695</a>, reported by benedikt.riedel and owned by olivas</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:11:45",
"description": "trigger-sim broken for frame objects that are not in simclasses or dataclasses. Found this because trunk trigger-sim does not work for GENIE simulation. GENIE puts the `I3GENIEResultsDict` in the frame. When trigger-sim loops through the frame objects to find the `I3TriggerHierarchy`, python will hit the `I3GENIEResultsDict` in the frame and will throw an `Unregistred Class` error because the `I3GENIEResultsDict` is not part of dataclasses or simclasses.\n\nIt is a bad idea to assume that everything in a frame is deserializable. The correct solution is to pass a list of `I3TriggerHierarchy`s and have a default that covers the standard use case. ",
"reporter": "benedikt.riedel",
"cc": "kclark, melanie.day",
"resolution": "fixed",
"_ts": "1550067105393059",
"component": "combo simulation",
"summary": "trigger-sim broken for frame objects that are not in simclasses or dataclasses",
"priority": "blocker",
"keywords": "",
"time": "2016-05-06T21:42:14",
"milestone": "",
"owner": "olivas",
"type": "defect"
}
```
</p>
</details>
| 1.0 | trigger-sim broken for frame objects that are not in simclasses or dataclasses (Trac #1695) - trigger-sim broken for frame objects that are not in simclasses or dataclasses. Found this because trunk trigger-sim does not work for GENIE simulation. GENIE puts the `I3GENIEResultsDict` in the frame. When trigger-sim loops through the frame objects to find the `I3TriggerHierarchy`, python will hit the `I3GENIEResultsDict` in the frame and will throw an `Unregistred Class` error because the `I3GENIEResultsDict` is not part of dataclasses or simclasses.
It is a bad idea to assume that everything in a frame is deserializable. The correct solution is to pass a list of `I3TriggerHierarchy`s and have a default that covers the standard use case.
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1695">https://code.icecube.wisc.edu/ticket/1695</a>, reported by benedikt.riedel and owned by olivas</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:11:45",
"description": "trigger-sim broken for frame objects that are not in simclasses or dataclasses. Found this because trunk trigger-sim does not work for GENIE simulation. GENIE puts the `I3GENIEResultsDict` in the frame. When trigger-sim loops through the frame objects to find the `I3TriggerHierarchy`, python will hit the `I3GENIEResultsDict` in the frame and will throw an `Unregistred Class` error because the `I3GENIEResultsDict` is not part of dataclasses or simclasses.\n\nIt is a bad idea to assume that everything in a frame is deserializable. The correct solution is to pass a list of `I3TriggerHierarchy`s and have a default that covers the standard use case. ",
"reporter": "benedikt.riedel",
"cc": "kclark, melanie.day",
"resolution": "fixed",
"_ts": "1550067105393059",
"component": "combo simulation",
"summary": "trigger-sim broken for frame objects that are not in simclasses or dataclasses",
"priority": "blocker",
"keywords": "",
"time": "2016-05-06T21:42:14",
"milestone": "",
"owner": "olivas",
"type": "defect"
}
```
</p>
</details>
| defect | trigger sim broken for frame objects that are not in simclasses or dataclasses trac trigger sim broken for frame objects that are not in simclasses or dataclasses found this because trunk trigger sim does not work for genie simulation genie puts the in the frame when trigger sim loops through the frame objects to find the python will hit the in the frame and will throw an unregistred class error because the is not part of dataclasses or simclasses it is a bad idea to assume that everything in a frame is deserializable the correct solution is to pass a list of s and have a default that covers the standard use case migrated from json status closed changetime description trigger sim broken for frame objects that are not in simclasses or dataclasses found this because trunk trigger sim does not work for genie simulation genie puts the in the frame when trigger sim loops through the frame objects to find the python will hit the in the frame and will throw an unregistred class error because the is not part of dataclasses or simclasses n nit is a bad idea to assume that everything in a frame is deserializable the correct solution is to pass a list of s and have a default that covers the standard use case reporter benedikt riedel cc kclark melanie day resolution fixed ts component combo simulation summary trigger sim broken for frame objects that are not in simclasses or dataclasses priority blocker keywords time milestone owner olivas type defect | 1 |
47,367 | 13,056,146,378 | IssuesEvent | 2020-07-30 03:48:00 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | closed | missing libraries (tools) from make tarball target (Trac #431) | Migrated from Trac combo core defect | Both libarchive.so* and liblzma.so* are omitted in the packing of the tarball. Loading of modules that link to these libraries fail at execution time.
Migrated from https://code.icecube.wisc.edu/ticket/431
```json
{
"status": "closed",
"changetime": "2012-10-31T20:26:48",
"description": "Both libarchive.so* and liblzma.so* are omitted in the packing of the tarball. Loading of modules that link to these libraries fail at execution time.",
"reporter": "juancarlos",
"cc": "",
"resolution": "fixed",
"_ts": "1351715208000000",
"component": "combo core",
"summary": "missing libraries (tools) from make tarball target",
"priority": "normal",
"keywords": "",
"time": "2012-07-12T16:06:30",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
| 1.0 | missing libraries (tools) from make tarball target (Trac #431) - Both libarchive.so* and liblzma.so* are omitted in the packing of the tarball. Loading of modules that link to these libraries fail at execution time.
Migrated from https://code.icecube.wisc.edu/ticket/431
```json
{
"status": "closed",
"changetime": "2012-10-31T20:26:48",
"description": "Both libarchive.so* and liblzma.so* are omitted in the packing of the tarball. Loading of modules that link to these libraries fail at execution time.",
"reporter": "juancarlos",
"cc": "",
"resolution": "fixed",
"_ts": "1351715208000000",
"component": "combo core",
"summary": "missing libraries (tools) from make tarball target",
"priority": "normal",
"keywords": "",
"time": "2012-07-12T16:06:30",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
| defect | missing libraries tools from make tarball target trac both libarchive so and liblzma so are omitted in the packing of the tarball loading of modules that link to these libraries fail at execution time migrated from json status closed changetime description both libarchive so and liblzma so are omitted in the packing of the tarball loading of modules that link to these libraries fail at execution time reporter juancarlos cc resolution fixed ts component combo core summary missing libraries tools from make tarball target priority normal keywords time milestone owner nega type defect | 1 |
19,273 | 3,175,866,801 | IssuesEvent | 2015-09-24 03:53:20 | jimradford/superputty | https://api.github.com/repos/jimradford/superputty | closed | how to remove the putty security key alert | auto-migrated Priority-Medium Type-Defect | ```
Everytime if i open a putty,its asking for putty security alert,let me know the
procedure to remove the option.
```
Original issue reported on code.google.com by `words2...@gmail.com` on 8 Nov 2013 at 9:40
Attachments:
* [security key alert.JPG](https://storage.googleapis.com/google-code-attachments/superputty/issue-391/comment-0/security key alert.JPG)
| 1.0 | how to remove the putty security key alert - ```
Everytime if i open a putty,its asking for putty security alert,let me know the
procedure to remove the option.
```
Original issue reported on code.google.com by `words2...@gmail.com` on 8 Nov 2013 at 9:40
Attachments:
* [security key alert.JPG](https://storage.googleapis.com/google-code-attachments/superputty/issue-391/comment-0/security key alert.JPG)
| defect | how to remove the putty security key alert everytime if i open a putty its asking for putty security alert let me know the procedure to remove the option original issue reported on code google com by gmail com on nov at attachments key alert jpg | 1 |
38,326 | 8,759,427,498 | IssuesEvent | 2018-12-15 16:06:10 | jsslutils/jsslutils | https://api.github.com/repos/jsslutils/jsslutils | closed | X509SSLContextFactory doesn't read org.jsslutils.prop.keyPassword property | Priority-Medium Type-Defect auto-migrated | ```
What steps will reproduce the problem?
1. Configure X509SSLContextFactory through no-arg constructor and configure
2. Get sslContext
3. Get java.security.UnrecoverableKeyException: Password must not be null
What is the expected output? What do you see instead?
I expect that setting the org.jsslutils.prop.keyPassword would perform the
same functionality as 'setKeyPassword(char[])', but it never calls it
What version of the product are you using? On what operating system?
1.0.5 on a Mac
Please provide any additional information below.
```
Original issue reported on code.google.com by `prad...@gmail.com` on 4 Mar 2011 at 9:46
| 1.0 | X509SSLContextFactory doesn't read org.jsslutils.prop.keyPassword property - ```
What steps will reproduce the problem?
1. Configure X509SSLContextFactory through no-arg constructor and configure
2. Get sslContext
3. Get java.security.UnrecoverableKeyException: Password must not be null
What is the expected output? What do you see instead?
I expect that setting the org.jsslutils.prop.keyPassword would perform the
same functionality as 'setKeyPassword(char[])', but it never calls it
What version of the product are you using? On what operating system?
1.0.5 on a Mac
Please provide any additional information below.
```
Original issue reported on code.google.com by `prad...@gmail.com` on 4 Mar 2011 at 9:46
| defect | doesn t read org jsslutils prop keypassword property what steps will reproduce the problem configure through no arg constructor and configure get sslcontext get java security unrecoverablekeyexception password must not be null what is the expected output what do you see instead i expect that setting the org jsslutils prop keypassword would perform the same functionality as setkeypassword char but it never calls it what version of the product are you using on what operating system on a mac please provide any additional information below original issue reported on code google com by prad gmail com on mar at | 1 |
10,221 | 2,618,942,682 | IssuesEvent | 2015-03-03 00:04:44 | marmarek/test | https://api.github.com/repos/marmarek/test | opened | modifier keys not handled correctly | C: gui-virtualization P: critical R: fixed T: defect | **Reported by joanna on 20 Oct 40373980 02:13 UTC**
When a user presses one of the modifier keys (Ctrl, Alt, Shift) and then change focus to another appviewer window, belonging to a *different* AppVM, but still while holding the modifier key, then when returning to the original VM, it will consider the modifier key never been released and would interpret all the subsequent keystrokes as if entered together with the modifier key (that currently is not down).
Proposed solution: Check the status of all the modifier keys when an appviewer window obtains focus, and send key_down messages if necessary.
Migrated-From: https://wiki.qubes-os.org/ticket/36 | 1.0 | modifier keys not handled correctly - **Reported by joanna on 20 Oct 40373980 02:13 UTC**
When a user presses one of the modifier keys (Ctrl, Alt, Shift) and then change focus to another appviewer window, belonging to a *different* AppVM, but still while holding the modifier key, then when returning to the original VM, it will consider the modifier key never been released and would interpret all the subsequent keystrokes as if entered together with the modifier key (that currently is not down).
Proposed solution: Check the status of all the modifier keys when an appviewer window obtains focus, and send key_down messages if necessary.
Migrated-From: https://wiki.qubes-os.org/ticket/36 | defect | modifier keys not handled correctly reported by joanna on oct utc when a user presses one of the modifier keys ctrl alt shift and then change focus to another appviewer window belonging to a different appvm but still while holding the modifier key then when returning to the original vm it will consider the modifier key never been released and would interpret all the subsequent keystrokes as if entered together with the modifier key that currently is not down proposed solution check the status of all the modifier keys when an appviewer window obtains focus and send key down messages if necessary migrated from | 1 |
34,242 | 7,431,748,775 | IssuesEvent | 2018-03-25 17:43:45 | Yahkal/replicaisland | https://api.github.com/repos/Yahkal/replicaisland | closed | Replicaisland show no wanda on my platform which does not support "draw_texture" gl extension. | Priority-Medium Type-Defect auto-migrated | ```
What steps will reproduce the problem?
1. Run the game, can't see cartoon people wanda.
2.
3.
What is the expected output? What do you see instead?
Should see the cartoon people.
What version of the product are you using? On what operating system?
The opengles on my platform doesn't support "draw_texture" extention.
So glDrawTexfOES will show nothing in DrawableBitmap.java.
As in GameRender.java, we have dected whether "draw_texture" is supported, we
should use other method to draw the texture in DrawableBitmap.java if this
extenstion is not supported by the hardware.
Please provide any additional information below.
I try to use glDrawArray for the texture, but still show nothing, may need your
help, the code is like below in DrawableBitmap.java:
/*((GL11Ext) gl).glDrawTexfOES(snappedX * scaleX, snappedY * scaleY,
getPriority(), width * scaleX, height * scaleY);*/
// test use glDrawElements
FloatBuffer vertexBuffer = ByteBuffer.allocateDirect(4 * 4 * 3).order(ByteOrder.nativeOrder()).asFloatBuffer();
FloatBuffer texBuffer = ByteBuffer.allocateDirect(4 * 4 * 3).order(ByteOrder.nativeOrder()).asFloatBuffer();
float ver_x = snappedX * scaleX;
float ver_y = snappedY * scaleY;
float ver_z = getPriority();
float w = width * scaleX;
float h = height * scaleY;
vertexBuffer.put(0 * 3, ver_x);
vertexBuffer.put(0 * 3 + 1, ver_y);
vertexBuffer.put(0 * 3 + 2, ver_z);
vertexBuffer.put(1 * 3, ver_x);
vertexBuffer.put(1 * 3 + 1, ver_y + h);
vertexBuffer.put(1 * 3 + 2, ver_z);
vertexBuffer.put(2 * 3, ver_x + w);
vertexBuffer.put(2 * 3 + 1, ver_y + h);
vertexBuffer.put(2 * 3 + 2, ver_z);
vertexBuffer.put(3 * 3, ver_x + w);
vertexBuffer.put(3 * 3 + 1, ver_y);
vertexBuffer.put(3 * 3 + 2, ver_z);
// mCrop[0]-[3]:u,v,w,h
texBuffer.put(0 * 2, mCrop[0] / mTexture.width );
texBuffer.put(0 * 2 + 1, mCrop[1] / mTexture.height);
texBuffer.put(1 * 2, mCrop[0] / mTexture.width);
texBuffer.put(1 * 2 + 1, (mCrop[1] + mCrop[3]) / mTexture.height);
texBuffer.put(2 * 2, (mCrop[0] + mCrop[2]) / mTexture.width);
texBuffer.put(2 * 2 + 1, (mCrop[1] + mCrop[3]) / mTexture.height);
texBuffer.put(3 * 2, (mCrop[0] + mCrop[2]) / mTexture.width);
texBuffer.put(3 * 2 + 1, mCrop[1] / mTexture.height);
gl.glVertexPointer(3, GL10.GL_FLOAT, 0, vertexBuffer);
int err = gl.glGetError();
if (err != GL10.GL_NO_ERROR) {
Log.e("vertexpointer", GLU.gluErrorString(err));
}
gl.glTexCoordPointer(2, GL10.GL_FLOAT, 0, texBuffer);
err = gl.glGetError();
if (err != GL10.GL_NO_ERROR) {
Log.e("vertexpointer", GLU.gluErrorString(err));
}
gl.glDrawArrays(GL10.GL_TRIANGLE_FAN, 0, 4);
err = gl.glGetError();
if (err != GL10.GL_NO_ERROR) {
Log.e("vertexpointer", GLU.gluErrorString(err));
}
```
Original issue reported on code.google.com by `yangjin0...@gmail.com` on 9 Aug 2011 at 3:45
| 1.0 | Replicaisland show no wanda on my platform which does not support "draw_texture" gl extension. - ```
What steps will reproduce the problem?
1. Run the game, can't see cartoon people wanda.
2.
3.
What is the expected output? What do you see instead?
Should see the cartoon people.
What version of the product are you using? On what operating system?
The opengles on my platform doesn't support "draw_texture" extention.
So glDrawTexfOES will show nothing in DrawableBitmap.java.
As in GameRender.java, we have dected whether "draw_texture" is supported, we
should use other method to draw the texture in DrawableBitmap.java if this
extenstion is not supported by the hardware.
Please provide any additional information below.
I try to use glDrawArray for the texture, but still show nothing, may need your
help, the code is like below in DrawableBitmap.java:
/*((GL11Ext) gl).glDrawTexfOES(snappedX * scaleX, snappedY * scaleY,
getPriority(), width * scaleX, height * scaleY);*/
// test use glDrawElements
FloatBuffer vertexBuffer = ByteBuffer.allocateDirect(4 * 4 * 3).order(ByteOrder.nativeOrder()).asFloatBuffer();
FloatBuffer texBuffer = ByteBuffer.allocateDirect(4 * 4 * 3).order(ByteOrder.nativeOrder()).asFloatBuffer();
float ver_x = snappedX * scaleX;
float ver_y = snappedY * scaleY;
float ver_z = getPriority();
float w = width * scaleX;
float h = height * scaleY;
vertexBuffer.put(0 * 3, ver_x);
vertexBuffer.put(0 * 3 + 1, ver_y);
vertexBuffer.put(0 * 3 + 2, ver_z);
vertexBuffer.put(1 * 3, ver_x);
vertexBuffer.put(1 * 3 + 1, ver_y + h);
vertexBuffer.put(1 * 3 + 2, ver_z);
vertexBuffer.put(2 * 3, ver_x + w);
vertexBuffer.put(2 * 3 + 1, ver_y + h);
vertexBuffer.put(2 * 3 + 2, ver_z);
vertexBuffer.put(3 * 3, ver_x + w);
vertexBuffer.put(3 * 3 + 1, ver_y);
vertexBuffer.put(3 * 3 + 2, ver_z);
// mCrop[0]-[3]:u,v,w,h
texBuffer.put(0 * 2, mCrop[0] / mTexture.width );
texBuffer.put(0 * 2 + 1, mCrop[1] / mTexture.height);
texBuffer.put(1 * 2, mCrop[0] / mTexture.width);
texBuffer.put(1 * 2 + 1, (mCrop[1] + mCrop[3]) / mTexture.height);
texBuffer.put(2 * 2, (mCrop[0] + mCrop[2]) / mTexture.width);
texBuffer.put(2 * 2 + 1, (mCrop[1] + mCrop[3]) / mTexture.height);
texBuffer.put(3 * 2, (mCrop[0] + mCrop[2]) / mTexture.width);
texBuffer.put(3 * 2 + 1, mCrop[1] / mTexture.height);
gl.glVertexPointer(3, GL10.GL_FLOAT, 0, vertexBuffer);
int err = gl.glGetError();
if (err != GL10.GL_NO_ERROR) {
Log.e("vertexpointer", GLU.gluErrorString(err));
}
gl.glTexCoordPointer(2, GL10.GL_FLOAT, 0, texBuffer);
err = gl.glGetError();
if (err != GL10.GL_NO_ERROR) {
Log.e("vertexpointer", GLU.gluErrorString(err));
}
gl.glDrawArrays(GL10.GL_TRIANGLE_FAN, 0, 4);
err = gl.glGetError();
if (err != GL10.GL_NO_ERROR) {
Log.e("vertexpointer", GLU.gluErrorString(err));
}
```
Original issue reported on code.google.com by `yangjin0...@gmail.com` on 9 Aug 2011 at 3:45
| defect | replicaisland show no wanda on my platform which does not support draw texture gl extension what steps will reproduce the problem run the game can t see cartoon people wanda what is the expected output what do you see instead should see the cartoon people what version of the product are you using on what operating system the opengles on my platform doesn t support draw texture extention so gldrawtexfoes will show nothing in drawablebitmap java as in gamerender java we have dected whether draw texture is supported we should use other method to draw the texture in drawablebitmap java if this extenstion is not supported by the hardware please provide any additional information below i try to use gldrawarray for the texture but still show nothing may need your help the code is like below in drawablebitmap java gl gldrawtexfoes snappedx scalex snappedy scaley getpriority width scalex height scaley test use gldrawelements floatbuffer vertexbuffer bytebuffer allocatedirect order byteorder nativeorder asfloatbuffer floatbuffer texbuffer bytebuffer allocatedirect order byteorder nativeorder asfloatbuffer float ver x snappedx scalex float ver y snappedy scaley float ver z getpriority float w width scalex float h height scaley vertexbuffer put ver x vertexbuffer put ver y vertexbuffer put ver z vertexbuffer put ver x vertexbuffer put ver y h vertexbuffer put ver z vertexbuffer put ver x w vertexbuffer put ver y h vertexbuffer put ver z vertexbuffer put ver x w vertexbuffer put ver y vertexbuffer put ver z mcrop u v w h texbuffer put mcrop mtexture width texbuffer put mcrop mtexture height texbuffer put mcrop mtexture width texbuffer put mcrop mcrop mtexture height texbuffer put mcrop mcrop mtexture width texbuffer put mcrop mcrop mtexture height texbuffer put mcrop mcrop mtexture width texbuffer put mcrop mtexture height gl glvertexpointer gl float vertexbuffer int err gl glgeterror if err gl no error log e vertexpointer glu gluerrorstring err gl gltexcoordpointer gl float texbuffer err gl glgeterror if err gl no error log e vertexpointer glu gluerrorstring err gl gldrawarrays gl triangle fan err gl glgeterror if err gl no error log e vertexpointer glu gluerrorstring err original issue reported on code google com by gmail com on aug at | 1 |
174,288 | 6,538,861,209 | IssuesEvent | 2017-09-01 08:36:07 | metoppv/improver | https://api.github.com/repos/metoppv/improver | closed | Time weighting functionality | Category: User Story Priority: High Size: 5 | Prerequisite #202
As the product owner I want IMPROVER to have the capability to include times outside the time of interest or the time window of interest in the generation of probabilities.
Here we will use the triangular weighting function written in #202.
Two variations of this are needed
1. A weighted probability was included in the demo suite and this should be incorporated into IMPROVER (unless it has already)
2. There is also a requirement to find the weighted maximum in the time window in order to give a more appropriate probability for the occurrence at a time if the exact timing doesn't matter. Here we are asking: what is the probability of an occurrence sometime around a time or period of interest?
For example, if a high probability is given that it will rain at 15.00 and it starts to rain at 15.10 (or stops at 14.50), that is still a decent forecast for most people. Or if the probability is specifically stated to be the probability that rain will occur sometime around 15.00 then, again, it is a decent forecast. Or it might be giving a non-zero probability of rain occurring sometime within the time period 12.00 to 18.00 and it rains at 18.10.
Document about time windows for precipitation accumulations:
[time_windowing_accumulations.pdf](https://github.com/metoppv/improver/files/1161842/time_windowing_accumulations.pdf)
Task 1:
To incorporate the time weighting used in the demo suite into IMPROVER. This is a triangular weighting function centred around the time of interest or a period of time. It can be applied either before or after neighbourhood processing. The probability of occurrence is the **mean** of all the time-weighted probabilities.
Task 2:
As for task 1, except that the probability of occurrence is the **maximum** of all the time-weighted probabilities.
Acceptance criteria:
* Unit tests
* Triangular time-based weighting support in `improver weighted-blending`
* Acceptance test for above
* [ NOT ESTIMATED ] Separate utility to find the maximum for each grid cell across a set of input files `improver stats --max`? Bash script using nco tools?
* Acceptance test for above
-------------------------------------------------------------------------------------------------------------------
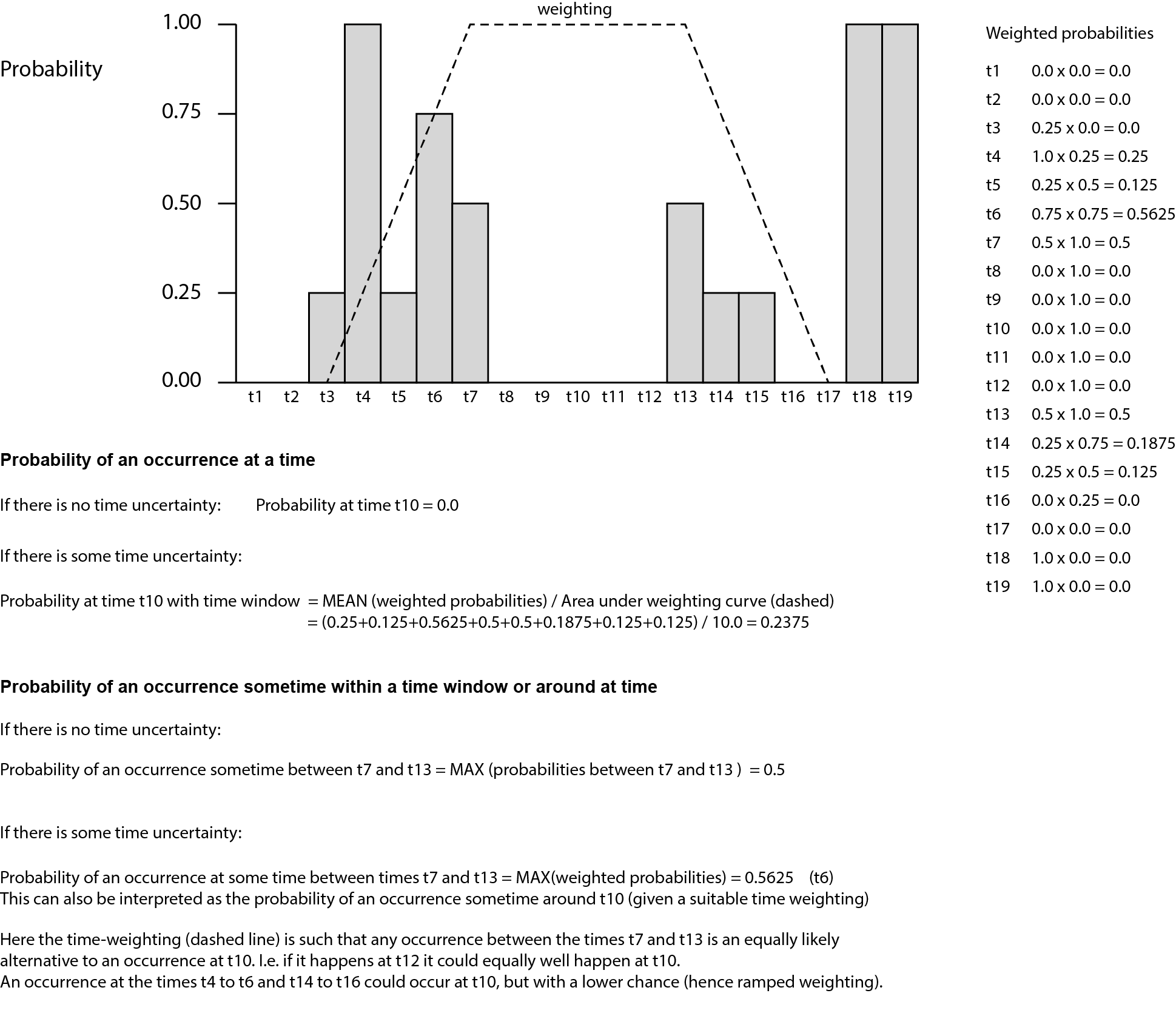
| 1.0 | Time weighting functionality - Prerequisite #202
As the product owner I want IMPROVER to have the capability to include times outside the time of interest or the time window of interest in the generation of probabilities.
Here we will use the triangular weighting function written in #202.
Two variations of this are needed
1. A weighted probability was included in the demo suite and this should be incorporated into IMPROVER (unless it has already)
2. There is also a requirement to find the weighted maximum in the time window in order to give a more appropriate probability for the occurrence at a time if the exact timing doesn't matter. Here we are asking: what is the probability of an occurrence sometime around a time or period of interest?
For example, if a high probability is given that it will rain at 15.00 and it starts to rain at 15.10 (or stops at 14.50), that is still a decent forecast for most people. Or if the probability is specifically stated to be the probability that rain will occur sometime around 15.00 then, again, it is a decent forecast. Or it might be giving a non-zero probability of rain occurring sometime within the time period 12.00 to 18.00 and it rains at 18.10.
Document about time windows for precipitation accumulations:
[time_windowing_accumulations.pdf](https://github.com/metoppv/improver/files/1161842/time_windowing_accumulations.pdf)
Task 1:
To incorporate the time weighting used in the demo suite into IMPROVER. This is a triangular weighting function centred around the time of interest or a period of time. It can be applied either before or after neighbourhood processing. The probability of occurrence is the **mean** of all the time-weighted probabilities.
Task 2:
As for task 1, except that the probability of occurrence is the **maximum** of all the time-weighted probabilities.
Acceptance criteria:
* Unit tests
* Triangular time-based weighting support in `improver weighted-blending`
* Acceptance test for above
* [ NOT ESTIMATED ] Separate utility to find the maximum for each grid cell across a set of input files `improver stats --max`? Bash script using nco tools?
* Acceptance test for above
-------------------------------------------------------------------------------------------------------------------
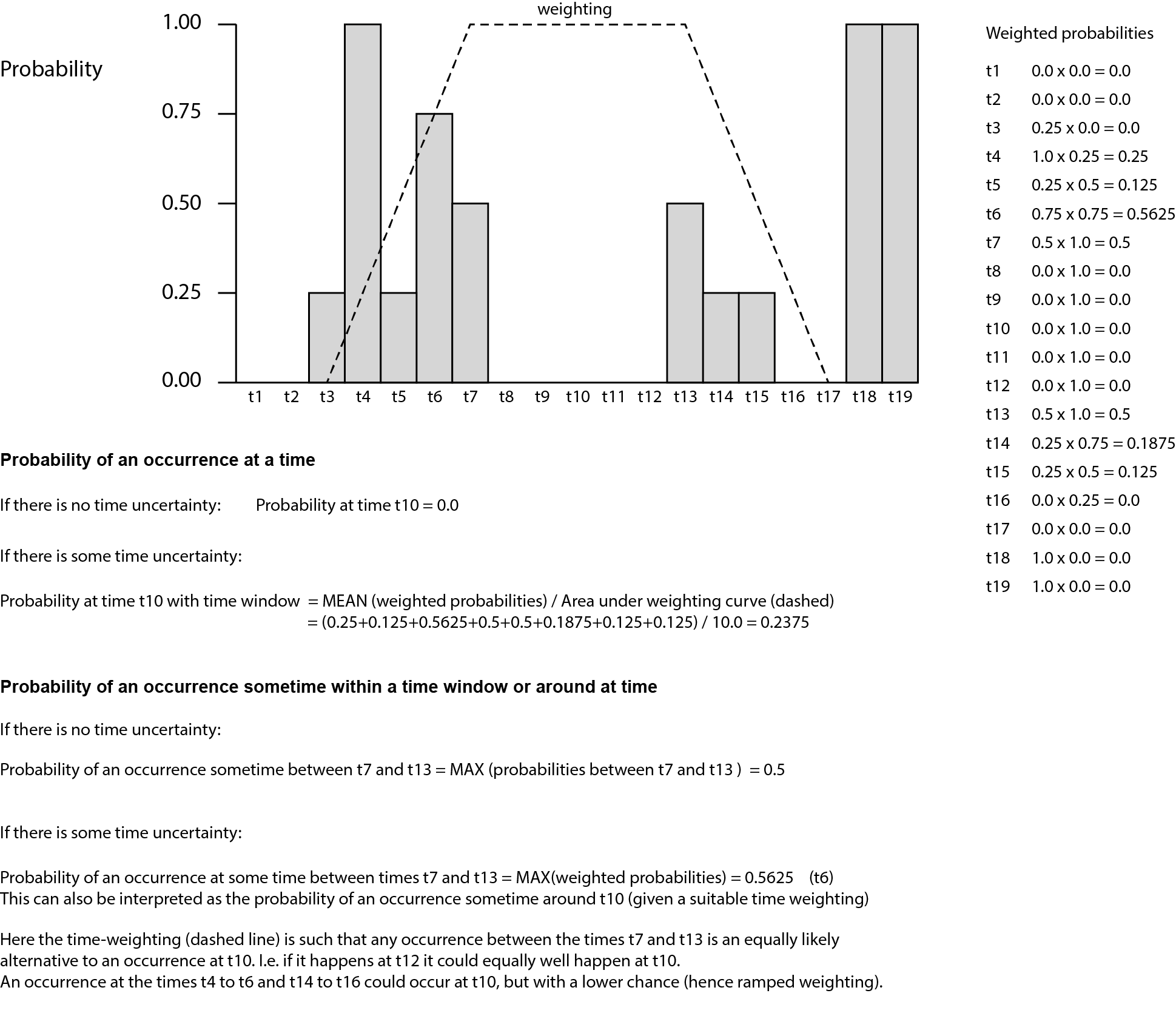
| non_defect | time weighting functionality prerequisite as the product owner i want improver to have the capability to include times outside the time of interest or the time window of interest in the generation of probabilities here we will use the triangular weighting function written in two variations of this are needed a weighted probability was included in the demo suite and this should be incorporated into improver unless it has already there is also a requirement to find the weighted maximum in the time window in order to give a more appropriate probability for the occurrence at a time if the exact timing doesn t matter here we are asking what is the probability of an occurrence sometime around a time or period of interest for example if a high probability is given that it will rain at and it starts to rain at or stops at that is still a decent forecast for most people or if the probability is specifically stated to be the probability that rain will occur sometime around then again it is a decent forecast or it might be giving a non zero probability of rain occurring sometime within the time period to and it rains at document about time windows for precipitation accumulations task to incorporate the time weighting used in the demo suite into improver this is a triangular weighting function centred around the time of interest or a period of time it can be applied either before or after neighbourhood processing the probability of occurrence is the mean of all the time weighted probabilities task as for task except that the probability of occurrence is the maximum of all the time weighted probabilities acceptance criteria unit tests triangular time based weighting support in improver weighted blending acceptance test for above separate utility to find the maximum for each grid cell across a set of input files improver stats max bash script using nco tools acceptance test for above | 0 |
76,549 | 26,485,238,296 | IssuesEvent | 2023-01-17 17:27:52 | dotCMS/core | https://api.github.com/repos/dotCMS/core | opened | Unconsistent icons | Type : Defect dotCMS : User Interface | [](https://mrkr.io/s/63c6da9711d6e78036d0372c/0)
## Problem Statement
There are filled icons and outlined icons, they all should be outlined, with rounded borders (Material Design Icons).
## Steps to Reproduce
## Acceptance Criteria
## Wireframes / Designs / Prototypes
## Testing Notes
## Assumptions
## Estimates
## Sub-Tasks
---
**Reported by:** Melissa Rojas Rodríguez (melissa.rojas@dotcms.com)
**Source URL:** [https://demo.dotcms.com/dotAdmin/#/content-types-angular](https://demo.dotcms.com/dotAdmin/#/content-types-angular)
**Issue details:** [Open in Marker.io](https://app.marker.io/i/63c6da9711d6e78036d0372f_05c24b098c191e39?advanced=1)
<table><tr><td><strong>Device type</strong></td><td>desktop</td></tr><tr><td><strong>Browser</strong></td><td>Chrome 108.0.0.0</td></tr><tr><td><strong>Screen Size</strong></td><td>1680 x 1050</td></tr><tr><td><strong>OS</strong></td><td>OS X 10.14.6</td></tr><tr><td><strong>Viewport Size</strong></td><td>1680 x 971</td></tr><tr><td><strong>Zoom Level</strong></td><td>100%</td></tr><tr><td><strong>Pixel Ratio</strong></td><td>@​2x</td></tr></table> | 1.0 | Unconsistent icons - [](https://mrkr.io/s/63c6da9711d6e78036d0372c/0)
## Problem Statement
There are filled icons and outlined icons, they all should be outlined, with rounded borders (Material Design Icons).
## Steps to Reproduce
## Acceptance Criteria
## Wireframes / Designs / Prototypes
## Testing Notes
## Assumptions
## Estimates
## Sub-Tasks
---
**Reported by:** Melissa Rojas Rodríguez (melissa.rojas@dotcms.com)
**Source URL:** [https://demo.dotcms.com/dotAdmin/#/content-types-angular](https://demo.dotcms.com/dotAdmin/#/content-types-angular)
**Issue details:** [Open in Marker.io](https://app.marker.io/i/63c6da9711d6e78036d0372f_05c24b098c191e39?advanced=1)
<table><tr><td><strong>Device type</strong></td><td>desktop</td></tr><tr><td><strong>Browser</strong></td><td>Chrome 108.0.0.0</td></tr><tr><td><strong>Screen Size</strong></td><td>1680 x 1050</td></tr><tr><td><strong>OS</strong></td><td>OS X 10.14.6</td></tr><tr><td><strong>Viewport Size</strong></td><td>1680 x 971</td></tr><tr><td><strong>Zoom Level</strong></td><td>100%</td></tr><tr><td><strong>Pixel Ratio</strong></td><td>@​2x</td></tr></table> | defect | unconsistent icons problem statement there are filled icons and outlined icons they all should be outlined with rounded borders material design icons steps to reproduce acceptance criteria wireframes designs prototypes testing notes assumptions estimates sub tasks reported by melissa rojas rodríguez melissa rojas dotcms com source url issue details device type desktop browser chrome screen size x os os x viewport size x zoom level pixel ratio | 1 |
17,746 | 3,012,952,898 | IssuesEvent | 2015-07-29 04:35:44 | yawlfoundation/yawl | https://api.github.com/repos/yawlfoundation/yawl | closed | ComboBoxes still editable when InputOnly | auto-migrated Component-Engine OpSys-All Priority-Medium Type-Defect | ```
What steps will reproduce the problem?
1. load the enclosed order fulfilment spec
2. create a po
What is the expected output? What do you see instead?
In 'approve po' none of the fields should be editable. But ComboBoxes are.
```
Original issue reported on code.google.com by `stephan....@googlemail.com` on 20 Feb 2009 at 8:17
Attachments:
* [orderfulfilment.yawl](https://storage.googleapis.com/google-code-attachments/yawl/issue-270/comment-0/orderfulfilment.yawl)
| 1.0 | ComboBoxes still editable when InputOnly - ```
What steps will reproduce the problem?
1. load the enclosed order fulfilment spec
2. create a po
What is the expected output? What do you see instead?
In 'approve po' none of the fields should be editable. But ComboBoxes are.
```
Original issue reported on code.google.com by `stephan....@googlemail.com` on 20 Feb 2009 at 8:17
Attachments:
* [orderfulfilment.yawl](https://storage.googleapis.com/google-code-attachments/yawl/issue-270/comment-0/orderfulfilment.yawl)
| defect | comboboxes still editable when inputonly what steps will reproduce the problem load the enclosed order fulfilment spec create a po what is the expected output what do you see instead in approve po none of the fields should be editable but comboboxes are original issue reported on code google com by stephan googlemail com on feb at attachments | 1 |
25,002 | 4,166,491,879 | IssuesEvent | 2016-06-20 03:45:42 | libarchive/libarchive | https://api.github.com/repos/libarchive/libarchive | closed | Invalid memory read on zip file in function trad_enc_decrypt_update() after entering empty password | OpSys-All Priority-Medium Type-Defect | Original [issue 415](https://code.google.com/p/libarchive/issues/detail?id=415) created by Google Code user `hanno@hboeck.de` on 2015-03-06T11:03:58.000Z:
```
bsdtar will detect the attached zip file as password protected. When entering nothing (just press enter) it will cause an invalid memory read access.
Found with american fuzzy lop.
==27792==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x631000010800 at pc 0x6169dd bp 0x7ffff41b2ef0 sp 0x7ffff41b2ee0
READ of size 1 at 0x631000010800 thread T0
#0 0x6169dc in trad_enc_decrypt_update libarchive/archive_read_support_format_zip.c:251
#1 0x6169dc in zip_read_data_none libarchive/archive_read_support_format_zip.c:1159
#2 0x6169dc in archive_read_format_zip_read_data libarchive/archive_read_support_format_zip.c:1797
#3 0x4a342d in copy_data libarchive/archive_read_extract2.c:139
#4 0x4a342d in archive_read_extract2 libarchive/archive_read_extract2.c:101
#5 0x41c088 in read_archive tar/read.c:361
#6 0x41d3ab in tar_mode_x tar/read.c:104
#7 0x40d4d9 in main tar/bsdtar.c:805
#8 0x7f83a55e6f9f in __libc_start_main (/lib64/libc.so.6+0x1ff9f)
#9 0x412d3c (/data/fuzzretest/bsdtar+0x412d3c)
0x631000010800 is located 0 bytes to the right of 65536-byte region [0x631000000800,0x631000010800)
allocated by thread T0 here:
#0 0x7f83a70cf6f7 in malloc (/usr/lib/gcc/x86_64-pc-linux-gnu/4.9.2/libasan.so.1+0x576f7)
#1 0x4a648c in file_open libarchive/archive_read_open_filename.c:358
```
See attachment: [pwcrash.zip](http://libarchive.github.io/google-code/issue-415/comment-0/pwcrash.zip)
See attachment: [pwcrash.zip.asan.txt](http://libarchive.github.io/google-code/issue-415/comment-0/pwcrash.zip.asan.txt) | 1.0 | Invalid memory read on zip file in function trad_enc_decrypt_update() after entering empty password - Original [issue 415](https://code.google.com/p/libarchive/issues/detail?id=415) created by Google Code user `hanno@hboeck.de` on 2015-03-06T11:03:58.000Z:
```
bsdtar will detect the attached zip file as password protected. When entering nothing (just press enter) it will cause an invalid memory read access.
Found with american fuzzy lop.
==27792==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x631000010800 at pc 0x6169dd bp 0x7ffff41b2ef0 sp 0x7ffff41b2ee0
READ of size 1 at 0x631000010800 thread T0
#0 0x6169dc in trad_enc_decrypt_update libarchive/archive_read_support_format_zip.c:251
#1 0x6169dc in zip_read_data_none libarchive/archive_read_support_format_zip.c:1159
#2 0x6169dc in archive_read_format_zip_read_data libarchive/archive_read_support_format_zip.c:1797
#3 0x4a342d in copy_data libarchive/archive_read_extract2.c:139
#4 0x4a342d in archive_read_extract2 libarchive/archive_read_extract2.c:101
#5 0x41c088 in read_archive tar/read.c:361
#6 0x41d3ab in tar_mode_x tar/read.c:104
#7 0x40d4d9 in main tar/bsdtar.c:805
#8 0x7f83a55e6f9f in __libc_start_main (/lib64/libc.so.6+0x1ff9f)
#9 0x412d3c (/data/fuzzretest/bsdtar+0x412d3c)
0x631000010800 is located 0 bytes to the right of 65536-byte region [0x631000000800,0x631000010800)
allocated by thread T0 here:
#0 0x7f83a70cf6f7 in malloc (/usr/lib/gcc/x86_64-pc-linux-gnu/4.9.2/libasan.so.1+0x576f7)
#1 0x4a648c in file_open libarchive/archive_read_open_filename.c:358
```
See attachment: [pwcrash.zip](http://libarchive.github.io/google-code/issue-415/comment-0/pwcrash.zip)
See attachment: [pwcrash.zip.asan.txt](http://libarchive.github.io/google-code/issue-415/comment-0/pwcrash.zip.asan.txt) | defect | invalid memory read on zip file in function trad enc decrypt update after entering empty password original created by google code user hanno hboeck de on bsdtar will detect the attached zip file as password protected when entering nothing just press enter it will cause an invalid memory read access found with american fuzzy lop error addresssanitizer heap buffer overflow on address at pc bp sp read of size at thread in trad enc decrypt update libarchive archive read support format zip c in zip read data none libarchive archive read support format zip c in archive read format zip read data libarchive archive read support format zip c in copy data libarchive archive read c in archive read libarchive archive read c in read archive tar read c in tar mode x tar read c in main tar bsdtar c in libc start main libc so data fuzzretest bsdtar is located bytes to the right of byte region allocated by thread here in malloc usr lib gcc pc linux gnu libasan so in file open libarchive archive read open filename c see attachment see attachment | 1 |
374,237 | 26,107,627,397 | IssuesEvent | 2022-12-27 15:10:33 | nextauthjs/next-auth | https://api.github.com/repos/nextauthjs/next-auth | closed | Github docs moved, links broken. | documentation triage | ### What is the improvement or update you wish to see?
In this commit https://github.com/nextauthjs/next-auth/commit/36f44a869a85a03ebe6e03d879615b352e0ef0b9 some files were deleted/moved.
CONTRIBUTING.MD for example has moved to
https://github.com/nextauthjs/.github/blob/main/CONTRIBUTING.md
There are still several references to the old file.
https://github.com/nextauthjs/next-auth/blob/511f66b0a8e4119e2e31ba16dcaf369488c9bca5/packages/next-auth/README.md?plain=1#L250
https://github.com/nextauthjs/next-auth/blob/511f66b0a8e4119e2e31ba16dcaf369488c9bca5/.github/PULL_REQUEST_TEMPLATE.md?plain=1#L32
https://github.com/nextauthjs/next-auth/blob/511f66b0a8e4119e2e31ba16dcaf369488c9bca5/docs/README.md?plain=1#L62
There are other files and links that need to be updated. I'm happy to open a PR if its just a matter of updating all the references to the new locations.
### Is there any context that might help us understand?
This looks like a bug but perhaps is being fixed by some tooling or automation process not yet implemented. I'm not familiar with some the tooling used here.
### Does the docs page already exist? Please link to it.
_No response_ | 1.0 | Github docs moved, links broken. - ### What is the improvement or update you wish to see?
In this commit https://github.com/nextauthjs/next-auth/commit/36f44a869a85a03ebe6e03d879615b352e0ef0b9 some files were deleted/moved.
CONTRIBUTING.MD for example has moved to
https://github.com/nextauthjs/.github/blob/main/CONTRIBUTING.md
There are still several references to the old file.
https://github.com/nextauthjs/next-auth/blob/511f66b0a8e4119e2e31ba16dcaf369488c9bca5/packages/next-auth/README.md?plain=1#L250
https://github.com/nextauthjs/next-auth/blob/511f66b0a8e4119e2e31ba16dcaf369488c9bca5/.github/PULL_REQUEST_TEMPLATE.md?plain=1#L32
https://github.com/nextauthjs/next-auth/blob/511f66b0a8e4119e2e31ba16dcaf369488c9bca5/docs/README.md?plain=1#L62
There are other files and links that need to be updated. I'm happy to open a PR if its just a matter of updating all the references to the new locations.
### Is there any context that might help us understand?
This looks like a bug but perhaps is being fixed by some tooling or automation process not yet implemented. I'm not familiar with some the tooling used here.
### Does the docs page already exist? Please link to it.
_No response_ | non_defect | github docs moved links broken what is the improvement or update you wish to see in this commit some files were deleted moved contributing md for example has moved to there are still several references to the old file there are other files and links that need to be updated i m happy to open a pr if its just a matter of updating all the references to the new locations is there any context that might help us understand this looks like a bug but perhaps is being fixed by some tooling or automation process not yet implemented i m not familiar with some the tooling used here does the docs page already exist please link to it no response | 0 |
61,436 | 17,023,693,677 | IssuesEvent | 2021-07-03 03:20:18 | tomhughes/trac-tickets | https://api.github.com/repos/tomhughes/trac-tickets | closed | White outline around streams | Component: mapnik Priority: minor Resolution: worksforme Type: defect | **[Submitted to the original trac issue database at 1.35am, Saturday, 2nd April 2011]**
All streams have a tiny white outline around them in Mapnik, which looks especially bad when streams run through forests or are routed through bodies of water. | 1.0 | White outline around streams - **[Submitted to the original trac issue database at 1.35am, Saturday, 2nd April 2011]**
All streams have a tiny white outline around them in Mapnik, which looks especially bad when streams run through forests or are routed through bodies of water. | defect | white outline around streams all streams have a tiny white outline around them in mapnik which looks especially bad when streams run through forests or are routed through bodies of water | 1 |
173,038 | 21,094,408,095 | IssuesEvent | 2022-04-04 08:57:43 | lukebroganws/WebGoat | https://api.github.com/repos/lukebroganws/WebGoat | closed | xstream-1.4.5.jar: 33 vulnerabilities (highest severity is: 9.9) - autoclosed | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.5.jar</b></p></summary>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>Library home page: <a href="http://codehaus.org/xstream-parent/xstream/">http://codehaus.org/xstream-parent/xstream/</a></p>
<p>Path to dependency file: /webgoat-integration-tests/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/WebGoat/commit/a6064aa05456a89cd27bf3951cddbee990e35520">a6064aa05456a89cd27bf3951cddbee990e35520</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-21345](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21345) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.9 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21344](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21344) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2013-7285](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-7285) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | xstream-1.4.5.jar | Direct | 1.4.7,1.4.11 | ✅ |
| [CVE-2021-21350](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21350) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21347](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21347) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21346](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21346) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21342](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21342) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.1 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21351](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21351) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.1 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-39139](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39139) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2020-26217](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26217) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.14 | ✅ |
| [CVE-2021-29505](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29505) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.17 | ✅ |
| [CVE-2021-21349](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21349) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.6 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-39150](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39150) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39152](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39152) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39151](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39151) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39154](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39154) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39153](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39153) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39141](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39141) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39145](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39145) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39144](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39144) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39147](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39147) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39146](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39146) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39149](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39149) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39148](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39148) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2020-26258](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26258) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.7 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.15 | ✅ |
| [CVE-2021-21343](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21343) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21341](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21341) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2017-7957](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7957) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | 1.4.10 | ✅ |
| [CVE-2016-3674](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-3674) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | 1.4.9 | ✅ |
| [CVE-2021-43859](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43859) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.19 | ✅ |
| [CVE-2021-21348](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21348) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2020-26259](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26259) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.15 | ✅ |
| [CVE-2021-39140](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39140) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.3 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
## Details
> Partial details (3 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the WhiteSource Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-21345</summary>
### Vulnerable Library - <b>xstream-1.4.5.jar</b></p>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>Library home page: <a href="http://codehaus.org/xstream-parent/xstream/">http://codehaus.org/xstream-parent/xstream/</a></p>
<p>Path to dependency file: /webgoat-integration-tests/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/WebGoat/commit/a6064aa05456a89cd27bf3951cddbee990e35520">a6064aa05456a89cd27bf3951cddbee990e35520</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker who has sufficient rights to execute commands of the host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream's security framework with a whitelist limited to the minimal required types. If you rely on XStream's default blacklist of the Security Framework, you will have to use at least version 1.4.16.
<p>Publish Date: 2021-03-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21345>CVE-2021-21345</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/x-stream/xstream/security/advisories/GHSA-hwpc-8xqv-jvj4">https://github.com/x-stream/xstream/security/advisories/GHSA-hwpc-8xqv-jvj4</a></p>
<p>Release Date: 2021-03-23</p>
<p>Fix Resolution: com.thoughtworks.xstream:xstream:1.4.16</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-21344</summary>
### Vulnerable Library - <b>xstream-1.4.5.jar</b></p>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>Library home page: <a href="http://codehaus.org/xstream-parent/xstream/">http://codehaus.org/xstream-parent/xstream/</a></p>
<p>Path to dependency file: /webgoat-integration-tests/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/WebGoat/commit/a6064aa05456a89cd27bf3951cddbee990e35520">a6064aa05456a89cd27bf3951cddbee990e35520</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream's security framework with a whitelist limited to the minimal required types. If you rely on XStream's default blacklist of the Security Framework, you will have to use at least version 1.4.16.
<p>Publish Date: 2021-03-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21344>CVE-2021-21344</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/x-stream/xstream/security/advisories/GHSA-59jw-jqf4-3wq3">https://github.com/x-stream/xstream/security/advisories/GHSA-59jw-jqf4-3wq3</a></p>
<p>Release Date: 2021-03-23</p>
<p>Fix Resolution: com.thoughtworks.xstream:xstream:1.4.16</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2013-7285</summary>
### Vulnerable Library - <b>xstream-1.4.5.jar</b></p>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>Library home page: <a href="http://codehaus.org/xstream-parent/xstream/">http://codehaus.org/xstream-parent/xstream/</a></p>
<p>Path to dependency file: /webgoat-integration-tests/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/WebGoat/commit/a6064aa05456a89cd27bf3951cddbee990e35520">a6064aa05456a89cd27bf3951cddbee990e35520</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Xstream API versions up to 1.4.6 and version 1.4.10, if the security framework has not been initialized, may allow a remote attacker to run arbitrary shell commands by manipulating the processed input stream when unmarshaling XML or any supported format. e.g. JSON.
<p>Publish Date: 2019-05-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-7285>CVE-2013-7285</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-7285">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-7285</a></p>
<p>Release Date: 2019-05-15</p>
<p>Fix Resolution: 1.4.7,1.4.11</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21345","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker who has sufficient rights to execute commands of the host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21345","cvss3Severity":"high","cvss3Score":"9.9","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21344","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21344","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.4.7,1.4.11","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2013-7285","vulnerabilityDetails":"Xstream API versions up to 1.4.6 and version 1.4.10, if the security framework has not been initialized, may allow a remote attacker to run arbitrary shell commands by manipulating the processed input stream when unmarshaling XML or any supported format. e.g. JSON.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-7285","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21350","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to execute arbitrary code only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21350","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21347","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21347","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21346","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21346","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21342","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability where the processed stream at unmarshalling time contains type information to recreate the formerly written objects. XStream creates therefore new instances based on these type information. An attacker can manipulate the processed input stream and replace or inject objects, that result in a server-side forgery request. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21342","cvss3Severity":"high","cvss3Score":"9.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21351","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21351","cvss3Severity":"high","cvss3Score":"9.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39139","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. A user is only affected if using the version out of the box with JDK 1.7u21 or below. However, this scenario can be adjusted easily to an external Xalan that works regardless of the version of the Java runtime. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39139","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.14","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2020-26217","vulnerabilityDetails":"XStream before version 1.4.14 is vulnerable to Remote Code Execution.The vulnerability may allow a remote attacker to run arbitrary shell commands only by manipulating the processed input stream. Only users who rely on blocklists are affected. Anyone using XStream\u0027s Security Framework allowlist is not affected. The linked advisory provides code workarounds for users who cannot upgrade. The issue is fixed in version 1.4.14.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26217","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.17","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-29505","vulnerabilityDetails":"XStream is software for serializing Java objects to XML and back again. A vulnerability in XStream versions prior to 1.4.17 may allow a remote attacker has sufficient rights to execute commands of the host only by manipulating the processed input stream. No user who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types is affected. The vulnerability is patched in version 1.4.17.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29505","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21349","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21349","cvss3Severity":"high","cvss3Score":"8.6","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39150","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream with a Java runtime version 14 to 8. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the [Security Framework](https://x-stream.github.io/security.html#framework), you will have to use at least version 1.4.18.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39150","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39152","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream with a Java runtime version 14 to 8. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the [Security Framework](https://x-stream.github.io/security.html#framework), you will have to use at least version 1.4.18.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39152","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39151","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39151","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39154","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39154","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39153","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream, if using the version out of the box with Java runtime version 14 to 8 or with JavaFX installed. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39153","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39141","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39141","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39145","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39145","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39144","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker has sufficient rights to execute commands of the host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39144","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39147","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39147","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39146","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39146","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39149","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39149","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39148","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39148","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.15","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2020-26258","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.15, a Server-Side Forgery Request vulnerability can be activated when unmarshalling. The vulnerability may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.15. The reported vulnerability does not exist if running Java 15 or higher. No user is affected who followed the recommendation to setup XStream\u0027s Security Framework with a whitelist! Anyone relying on XStream\u0027s default blacklist can immediately switch to a whilelist for the allowed types to avoid the vulnerability. Users of XStream 1.4.14 or below who still want to use XStream default blacklist can use a workaround described in more detailed in the referenced advisories.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26258","cvss3Severity":"high","cvss3Score":"7.7","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21343","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability where the processed stream at unmarshalling time contains type information to recreate the formerly written objects. XStream creates therefore new instances based on these type information. An attacker can manipulate the processed input stream and replace or inject objects, that result in the deletion of a file on the local host. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21343","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21341","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is vulnerability which may allow a remote attacker to allocate 100% CPU time on the target system depending on CPU type or parallel execution of such a payload resulting in a denial of service only by manipulating the processed input stream. No user is affected who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21341","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.4.10","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2017-7957","vulnerabilityDetails":"XStream through 1.4.9, when a certain denyTypes workaround is not used, mishandles attempts to create an instance of the primitive type \u0027void\u0027 during unmarshalling, leading to a remote application crash, as demonstrated by an xstream.fromXML(\"\u003cvoid/\u003e\") call.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7957","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.4.9","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2016-3674","vulnerabilityDetails":"Multiple XML external entity (XXE) vulnerabilities in the (1) Dom4JDriver, (2) DomDriver, (3) JDomDriver, (4) JDom2Driver, (5) SjsxpDriver, (6) StandardStaxDriver, and (7) WstxDriver drivers in XStream before 1.4.9 allow remote attackers to read arbitrary files via a crafted XML document.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-3674","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.19","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-43859","vulnerabilityDetails":"XStream is an open source java library to serialize objects to XML and back again. Versions prior to 1.4.19 may allow a remote attacker to allocate 100% CPU time on the target system depending on CPU type or parallel execution of such a payload resulting in a denial of service only by manipulating the processed input stream. XStream 1.4.19 monitors and accumulates the time it takes to add elements to collections and throws an exception if a set threshold is exceeded. Users are advised to upgrade as soon as possible. Users unable to upgrade may set the NO_REFERENCE mode to prevent recursion. See GHSA-rmr5-cpv2-vgjf for further details on a workaround if an upgrade is not possible.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43859","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21348","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to occupy a thread that consumes maximum CPU time and will never return. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21348","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.15","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2020-26259","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.15, is vulnerable to an Arbitrary File Deletion on the local host when unmarshalling. The vulnerability may allow a remote attacker to delete arbitrary know files on the host as log as the executing process has sufficient rights only by manipulating the processed input stream. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.15. The reported vulnerability does not exist running Java 15 or higher. No user is affected, who followed the recommendation to setup XStream\u0027s Security Framework with a whitelist! Anyone relying on XStream\u0027s default blacklist can immediately switch to a whilelist for the allowed types to avoid the vulnerability. Users of XStream 1.4.14 or below who still want to use XStream default blacklist can use a workaround described in more detailed in the referenced advisories.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26259","cvss3Severity":"medium","cvss3Score":"6.8","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Changed","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39140","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to allocate 100% CPU time on the target system depending on CPU type or parallel execution of such a payload resulting in a denial of service only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39140","cvss3Severity":"medium","cvss3Score":"6.3","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}]</REMEDIATE> --> | True | xstream-1.4.5.jar: 33 vulnerabilities (highest severity is: 9.9) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.5.jar</b></p></summary>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>Library home page: <a href="http://codehaus.org/xstream-parent/xstream/">http://codehaus.org/xstream-parent/xstream/</a></p>
<p>Path to dependency file: /webgoat-integration-tests/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/WebGoat/commit/a6064aa05456a89cd27bf3951cddbee990e35520">a6064aa05456a89cd27bf3951cddbee990e35520</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-21345](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21345) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.9 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21344](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21344) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2013-7285](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-7285) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | xstream-1.4.5.jar | Direct | 1.4.7,1.4.11 | ✅ |
| [CVE-2021-21350](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21350) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21347](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21347) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21346](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21346) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21342](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21342) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.1 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21351](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21351) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.1 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-39139](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39139) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2020-26217](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26217) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.14 | ✅ |
| [CVE-2021-29505](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29505) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.17 | ✅ |
| [CVE-2021-21349](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21349) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.6 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-39150](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39150) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39152](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39152) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39151](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39151) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39154](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39154) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39153](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39153) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39141](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39141) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39145](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39145) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39144](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39144) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39147](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39147) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39146](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39146) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39149](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39149) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39148](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39148) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2020-26258](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26258) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.7 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.15 | ✅ |
| [CVE-2021-21343](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21343) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21341](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21341) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2017-7957](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7957) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | 1.4.10 | ✅ |
| [CVE-2016-3674](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-3674) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | 1.4.9 | ✅ |
| [CVE-2021-43859](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43859) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.19 | ✅ |
| [CVE-2021-21348](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21348) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2020-26259](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26259) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.15 | ✅ |
| [CVE-2021-39140](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39140) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.3 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
## Details
> Partial details (3 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the WhiteSource Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-21345</summary>
### Vulnerable Library - <b>xstream-1.4.5.jar</b></p>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>Library home page: <a href="http://codehaus.org/xstream-parent/xstream/">http://codehaus.org/xstream-parent/xstream/</a></p>
<p>Path to dependency file: /webgoat-integration-tests/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/WebGoat/commit/a6064aa05456a89cd27bf3951cddbee990e35520">a6064aa05456a89cd27bf3951cddbee990e35520</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker who has sufficient rights to execute commands of the host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream's security framework with a whitelist limited to the minimal required types. If you rely on XStream's default blacklist of the Security Framework, you will have to use at least version 1.4.16.
<p>Publish Date: 2021-03-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21345>CVE-2021-21345</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/x-stream/xstream/security/advisories/GHSA-hwpc-8xqv-jvj4">https://github.com/x-stream/xstream/security/advisories/GHSA-hwpc-8xqv-jvj4</a></p>
<p>Release Date: 2021-03-23</p>
<p>Fix Resolution: com.thoughtworks.xstream:xstream:1.4.16</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-21344</summary>
### Vulnerable Library - <b>xstream-1.4.5.jar</b></p>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>Library home page: <a href="http://codehaus.org/xstream-parent/xstream/">http://codehaus.org/xstream-parent/xstream/</a></p>
<p>Path to dependency file: /webgoat-integration-tests/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/WebGoat/commit/a6064aa05456a89cd27bf3951cddbee990e35520">a6064aa05456a89cd27bf3951cddbee990e35520</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream's security framework with a whitelist limited to the minimal required types. If you rely on XStream's default blacklist of the Security Framework, you will have to use at least version 1.4.16.
<p>Publish Date: 2021-03-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21344>CVE-2021-21344</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/x-stream/xstream/security/advisories/GHSA-59jw-jqf4-3wq3">https://github.com/x-stream/xstream/security/advisories/GHSA-59jw-jqf4-3wq3</a></p>
<p>Release Date: 2021-03-23</p>
<p>Fix Resolution: com.thoughtworks.xstream:xstream:1.4.16</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2013-7285</summary>
### Vulnerable Library - <b>xstream-1.4.5.jar</b></p>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>Library home page: <a href="http://codehaus.org/xstream-parent/xstream/">http://codehaus.org/xstream-parent/xstream/</a></p>
<p>Path to dependency file: /webgoat-integration-tests/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/WebGoat/commit/a6064aa05456a89cd27bf3951cddbee990e35520">a6064aa05456a89cd27bf3951cddbee990e35520</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Xstream API versions up to 1.4.6 and version 1.4.10, if the security framework has not been initialized, may allow a remote attacker to run arbitrary shell commands by manipulating the processed input stream when unmarshaling XML or any supported format. e.g. JSON.
<p>Publish Date: 2019-05-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-7285>CVE-2013-7285</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-7285">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-7285</a></p>
<p>Release Date: 2019-05-15</p>
<p>Fix Resolution: 1.4.7,1.4.11</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21345","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker who has sufficient rights to execute commands of the host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21345","cvss3Severity":"high","cvss3Score":"9.9","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21344","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21344","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.4.7,1.4.11","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2013-7285","vulnerabilityDetails":"Xstream API versions up to 1.4.6 and version 1.4.10, if the security framework has not been initialized, may allow a remote attacker to run arbitrary shell commands by manipulating the processed input stream when unmarshaling XML or any supported format. e.g. JSON.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-7285","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21350","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to execute arbitrary code only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21350","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21347","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21347","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21346","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21346","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21342","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability where the processed stream at unmarshalling time contains type information to recreate the formerly written objects. XStream creates therefore new instances based on these type information. An attacker can manipulate the processed input stream and replace or inject objects, that result in a server-side forgery request. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21342","cvss3Severity":"high","cvss3Score":"9.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21351","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21351","cvss3Severity":"high","cvss3Score":"9.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39139","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. A user is only affected if using the version out of the box with JDK 1.7u21 or below. However, this scenario can be adjusted easily to an external Xalan that works regardless of the version of the Java runtime. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39139","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.14","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2020-26217","vulnerabilityDetails":"XStream before version 1.4.14 is vulnerable to Remote Code Execution.The vulnerability may allow a remote attacker to run arbitrary shell commands only by manipulating the processed input stream. Only users who rely on blocklists are affected. Anyone using XStream\u0027s Security Framework allowlist is not affected. The linked advisory provides code workarounds for users who cannot upgrade. The issue is fixed in version 1.4.14.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26217","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.17","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-29505","vulnerabilityDetails":"XStream is software for serializing Java objects to XML and back again. A vulnerability in XStream versions prior to 1.4.17 may allow a remote attacker has sufficient rights to execute commands of the host only by manipulating the processed input stream. No user who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types is affected. The vulnerability is patched in version 1.4.17.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29505","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21349","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21349","cvss3Severity":"high","cvss3Score":"8.6","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39150","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream with a Java runtime version 14 to 8. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the [Security Framework](https://x-stream.github.io/security.html#framework), you will have to use at least version 1.4.18.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39150","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39152","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream with a Java runtime version 14 to 8. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the [Security Framework](https://x-stream.github.io/security.html#framework), you will have to use at least version 1.4.18.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39152","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39151","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39151","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39154","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39154","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39153","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream, if using the version out of the box with Java runtime version 14 to 8 or with JavaFX installed. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39153","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39141","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39141","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39145","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39145","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39144","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker has sufficient rights to execute commands of the host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39144","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39147","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39147","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39146","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39146","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39149","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39149","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39148","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39148","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.15","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2020-26258","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.15, a Server-Side Forgery Request vulnerability can be activated when unmarshalling. The vulnerability may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.15. The reported vulnerability does not exist if running Java 15 or higher. No user is affected who followed the recommendation to setup XStream\u0027s Security Framework with a whitelist! Anyone relying on XStream\u0027s default blacklist can immediately switch to a whilelist for the allowed types to avoid the vulnerability. Users of XStream 1.4.14 or below who still want to use XStream default blacklist can use a workaround described in more detailed in the referenced advisories.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26258","cvss3Severity":"high","cvss3Score":"7.7","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21343","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability where the processed stream at unmarshalling time contains type information to recreate the formerly written objects. XStream creates therefore new instances based on these type information. An attacker can manipulate the processed input stream and replace or inject objects, that result in the deletion of a file on the local host. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21343","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21341","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is vulnerability which may allow a remote attacker to allocate 100% CPU time on the target system depending on CPU type or parallel execution of such a payload resulting in a denial of service only by manipulating the processed input stream. No user is affected who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21341","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.4.10","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2017-7957","vulnerabilityDetails":"XStream through 1.4.9, when a certain denyTypes workaround is not used, mishandles attempts to create an instance of the primitive type \u0027void\u0027 during unmarshalling, leading to a remote application crash, as demonstrated by an xstream.fromXML(\"\u003cvoid/\u003e\") call.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7957","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.4.9","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2016-3674","vulnerabilityDetails":"Multiple XML external entity (XXE) vulnerabilities in the (1) Dom4JDriver, (2) DomDriver, (3) JDomDriver, (4) JDom2Driver, (5) SjsxpDriver, (6) StandardStaxDriver, and (7) WstxDriver drivers in XStream before 1.4.9 allow remote attackers to read arbitrary files via a crafted XML document.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-3674","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.19","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-43859","vulnerabilityDetails":"XStream is an open source java library to serialize objects to XML and back again. Versions prior to 1.4.19 may allow a remote attacker to allocate 100% CPU time on the target system depending on CPU type or parallel execution of such a payload resulting in a denial of service only by manipulating the processed input stream. XStream 1.4.19 monitors and accumulates the time it takes to add elements to collections and throws an exception if a set threshold is exceeded. Users are advised to upgrade as soon as possible. Users unable to upgrade may set the NO_REFERENCE mode to prevent recursion. See GHSA-rmr5-cpv2-vgjf for further details on a workaround if an upgrade is not possible.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43859","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21348","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to occupy a thread that consumes maximum CPU time and will never return. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21348","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.15","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2020-26259","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.15, is vulnerable to an Arbitrary File Deletion on the local host when unmarshalling. The vulnerability may allow a remote attacker to delete arbitrary know files on the host as log as the executing process has sufficient rights only by manipulating the processed input stream. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.15. The reported vulnerability does not exist running Java 15 or higher. No user is affected, who followed the recommendation to setup XStream\u0027s Security Framework with a whitelist! Anyone relying on XStream\u0027s default blacklist can immediately switch to a whilelist for the allowed types to avoid the vulnerability. Users of XStream 1.4.14 or below who still want to use XStream default blacklist can use a workaround described in more detailed in the referenced advisories.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26259","cvss3Severity":"medium","cvss3Score":"6.8","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Changed","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":["/webgoat-integration-tests/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39140","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to allocate 100% CPU time on the target system depending on CPU type or parallel execution of such a payload resulting in a denial of service only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39140","cvss3Severity":"medium","cvss3Score":"6.3","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}]</REMEDIATE> --> | non_defect | xstream jar vulnerabilities highest severity is autoclosed vulnerable library xstream jar xstream is a serialization library from java objects to xml and back library home page a href path to dependency file webgoat integration tests pom xml path to vulnerable library home wss scanner repository com thoughtworks xstream xstream xstream jar home wss scanner repository com thoughtworks xstream xstream xstream jar repository com thoughtworks xstream xstream xstream jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream high xstream jar direct high xstream jar direct high xstream jar direct com thoughtworks xstream xstream high xstream jar direct com thoughtworks xstream xstream medium xstream jar direct com thoughtworks xstream xstream medium xstream jar direct com thoughtworks xstream xstream details partial details vulnerabilities are displayed below due to a content size limitation in github to view information on the remaining vulnerabilities navigate to the whitesource application cve vulnerable library xstream jar xstream is a serialization library from java objects to xml and back library home page a href path to dependency file webgoat integration tests pom xml path to vulnerable library home wss scanner repository com thoughtworks xstream xstream xstream jar home wss scanner repository com thoughtworks xstream xstream xstream jar repository com thoughtworks xstream xstream xstream jar dependency hierarchy x xstream jar vulnerable library found in head commit a href found in base branch develop vulnerability details xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker who has sufficient rights to execute commands of the host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream s security framework with a whitelist limited to the minimal required types if you rely on xstream s default blacklist of the security framework you will have to use at least version publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com thoughtworks xstream xstream rescue worker helmet automatic remediation is available for this issue cve vulnerable library xstream jar xstream is a serialization library from java objects to xml and back library home page a href path to dependency file webgoat integration tests pom xml path to vulnerable library home wss scanner repository com thoughtworks xstream xstream xstream jar home wss scanner repository com thoughtworks xstream xstream xstream jar repository com thoughtworks xstream xstream xstream jar dependency hierarchy x xstream jar vulnerable library found in head commit a href found in base branch develop vulnerability details xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream s security framework with a whitelist limited to the minimal required types if you rely on xstream s default blacklist of the security framework you will have to use at least version publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com thoughtworks xstream xstream rescue worker helmet automatic remediation is available for this issue cve vulnerable library xstream jar xstream is a serialization library from java objects to xml and back library home page a href path to dependency file webgoat integration tests pom xml path to vulnerable library home wss scanner repository com thoughtworks xstream xstream xstream jar home wss scanner repository com thoughtworks xstream xstream xstream jar repository com thoughtworks xstream xstream xstream jar dependency hierarchy x xstream jar vulnerable library found in head commit a href found in base branch develop vulnerability details xstream api versions up to and version if the security framework has not been initialized may allow a remote attacker to run arbitrary shell commands by manipulating the processed input stream when unmarshaling xml or any supported format e g json publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker who has sufficient rights to execute commands of the host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream api versions up to and version if the security framework has not been initialized may allow a remote attacker to run arbitrary shell commands by manipulating the processed input stream when unmarshaling xml or any supported format e g json vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker to execute arbitrary code only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability where the processed stream at unmarshalling time contains type information to recreate the formerly written objects xstream creates therefore new instances based on these type information an attacker can manipulate the processed input stream and replace or inject objects that result in a server side forgery request no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream a user is only affected if using the version out of the box with jdk or below however this scenario can be adjusted easily to an external xalan that works regardless of the version of the java runtime no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream before version is vulnerable to remote code execution the vulnerability may allow a remote attacker to run arbitrary shell commands only by manipulating the processed input stream only users who rely on blocklists are affected anyone using xstream security framework allowlist is not affected the linked advisory provides code workarounds for users who cannot upgrade the issue is fixed in version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is software for serializing java objects to xml and back again a vulnerability in xstream versions prior to may allow a remote attacker has sufficient rights to execute commands of the host only by manipulating the processed input stream no user who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types is affected the vulnerability is patched in version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream with a java runtime version to no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream with a java runtime version to no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream if using the version out of the box with java runtime version to or with javafx installed no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker has sufficient rights to execute commands of the host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version a server side forgery request vulnerability can be activated when unmarshalling the vulnerability may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream if you rely on xstream default blacklist of the security framework you will have to use at least version the reported vulnerability does not exist if running java or higher no user is affected who followed the recommendation to setup xstream security framework with a whitelist anyone relying on xstream default blacklist can immediately switch to a whilelist for the allowed types to avoid the vulnerability users of xstream or below who still want to use xstream default blacklist can use a workaround described in more detailed in the referenced advisories vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability where the processed stream at unmarshalling time contains type information to recreate the formerly written objects xstream creates therefore new instances based on these type information an attacker can manipulate the processed input stream and replace or inject objects that result in the deletion of a file on the local host no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is vulnerability which may allow a remote attacker to allocate cpu time on the target system depending on cpu type or parallel execution of such a payload resulting in a denial of service only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream through when a certain denytypes workaround is not used mishandles attempts to create an instance of the primitive type during unmarshalling leading to a remote application crash as demonstrated by an xstream fromxml call vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails multiple xml external entity xxe vulnerabilities in the domdriver jdomdriver sjsxpdriver standardstaxdriver and wstxdriver drivers in xstream before allow remote attackers to read arbitrary files via a crafted xml document vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is an open source java library to serialize objects to xml and back again versions prior to may allow a remote attacker to allocate cpu time on the target system depending on cpu type or parallel execution of such a payload resulting in a denial of service only by manipulating the processed input stream xstream monitors and accumulates the time it takes to add elements to collections and throws an exception if a set threshold is exceeded users are advised to upgrade as soon as possible users unable to upgrade may set the no reference mode to prevent recursion see ghsa vgjf for further details on a workaround if an upgrade is not possible vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker to occupy a thread that consumes maximum cpu time and will never return no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version is vulnerable to an arbitrary file deletion on the local host when unmarshalling the vulnerability may allow a remote attacker to delete arbitrary know files on the host as log as the executing process has sufficient rights only by manipulating the processed input stream if you rely on xstream default blacklist of the security framework you will have to use at least version the reported vulnerability does not exist running java or higher no user is affected who followed the recommendation to setup xstream security framework with a whitelist anyone relying on xstream default blacklist can immediately switch to a whilelist for the allowed types to avoid the vulnerability users of xstream or below who still want to use xstream default blacklist can use a workaround described in more detailed in the referenced advisories vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to allocate cpu time on the target system depending on cpu type or parallel execution of such a payload resulting in a denial of service only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl | 0 |
196,653 | 15,604,961,725 | IssuesEvent | 2021-03-19 05:07:35 | vuetifyjs/vuetify | https://api.github.com/repos/vuetifyjs/vuetify | closed | [Documentation] Content Quicklinks of v-calendar - Wrong scroll position | T: documentation good first issue | ### Environment
**Browsers:** Chrome 88.0.4324.190
**OS:** Windows 10
### Steps to reproduce
Click on Contents > Events
### Expected Behavior
Screen scrolls to the component events
### Actual Behavior
Screen scrolls to the property called "events"
### Reproduction Link
<a href="https://vuetifyjs.com/en/api/v-calendar/#events" target="_blank">https://vuetifyjs.com/en/api/v-calendar/#events</a>
<!-- generated by vuetify-issue-helper. DO NOT REMOVE --> | 1.0 | [Documentation] Content Quicklinks of v-calendar - Wrong scroll position - ### Environment
**Browsers:** Chrome 88.0.4324.190
**OS:** Windows 10
### Steps to reproduce
Click on Contents > Events
### Expected Behavior
Screen scrolls to the component events
### Actual Behavior
Screen scrolls to the property called "events"
### Reproduction Link
<a href="https://vuetifyjs.com/en/api/v-calendar/#events" target="_blank">https://vuetifyjs.com/en/api/v-calendar/#events</a>
<!-- generated by vuetify-issue-helper. DO NOT REMOVE --> | non_defect | content quicklinks of v calendar wrong scroll position environment browsers chrome os windows steps to reproduce click on contents events expected behavior screen scrolls to the component events actual behavior screen scrolls to the property called events reproduction link | 0 |
72,656 | 24,222,673,402 | IssuesEvent | 2022-09-26 12:12:20 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | closed | Jet remote IMap connector blocks in init() method | Type: Defect Source: Internal Team: SQL Module: Jet | Related to #21499. We need to workaround this before the issue is fixed. | 1.0 | Jet remote IMap connector blocks in init() method - Related to #21499. We need to workaround this before the issue is fixed. | defect | jet remote imap connector blocks in init method related to we need to workaround this before the issue is fixed | 1 |
105,984 | 13,236,718,623 | IssuesEvent | 2020-08-18 20:18:43 | phetsims/natural-selection | https://api.github.com/repos/phetsims/natural-selection | opened | recessive mutations should not be favored by environmental factors | design:general | This came up in the context of https://github.com/phetsims/natural-selection/issues/183, revising the Food model.
Recessive mutants are currently excluded from application of environmental factors. This can lead to incorrect conclusions, and odd behavior if recessive mutants are the sole remaining bunnies.
@amanda-phet and I discussed on Zoom, and decided that this behavior is incorrect. Recessive mutants can be favored during mating, to make them appear in the phenotype more quickly. But they should not be favored during selection.
I will change this. If we discover that it causes other problem, we can revisit, and it's relatively easy to revert. | 1.0 | recessive mutations should not be favored by environmental factors - This came up in the context of https://github.com/phetsims/natural-selection/issues/183, revising the Food model.
Recessive mutants are currently excluded from application of environmental factors. This can lead to incorrect conclusions, and odd behavior if recessive mutants are the sole remaining bunnies.
@amanda-phet and I discussed on Zoom, and decided that this behavior is incorrect. Recessive mutants can be favored during mating, to make them appear in the phenotype more quickly. But they should not be favored during selection.
I will change this. If we discover that it causes other problem, we can revisit, and it's relatively easy to revert. | non_defect | recessive mutations should not be favored by environmental factors this came up in the context of revising the food model recessive mutants are currently excluded from application of environmental factors this can lead to incorrect conclusions and odd behavior if recessive mutants are the sole remaining bunnies amanda phet and i discussed on zoom and decided that this behavior is incorrect recessive mutants can be favored during mating to make them appear in the phenotype more quickly but they should not be favored during selection i will change this if we discover that it causes other problem we can revisit and it s relatively easy to revert | 0 |
87,360 | 8,072,732,235 | IssuesEvent | 2018-08-06 16:54:01 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | distsql: tracking issue for continuous load tests | A-sql-execution A-testing C-performance | This is a tracking issue for the next phase of DistSQL continuous load testing. The goal is to test DistSQL more thoroughly, and eagerly raise any stability issues in DistSQL execution if there are any lurking under the hood.
#14288 was a success in identifying queries to empirically test in DistSQL, and #14295 was a success in identifying which TPC-H queries we could even run. We closed those issues as we got over the finish line for each query, getting them running in individual tests. It's time to step that up and run those queries under continuous, repetitive load on a production cluster, to see if we reveal any additional issues under stress.
The goal is to track two things:
1. That queries that we support do run repeatedly for weeks.
2. That queries that we don't support (e.g. data sets too big to be computed in-memory) fail gracefully without crashing cockroach nodes.
The cluster to be used for continuous load testing is Navy. Load will be monitored by me and @asubiotto. The load generator used will be `loadgen/tpch`.
The queries we will run are those TPC-H that were seen to work previously, namely:
* Query 1
* Query 3
* Query 7
* Query 8
* Query 9
* Query 15
* Query 19
We will initially run it on `scalefactor=5`, expecting success. We will then up the scalefactor until we abort every query due to OOM, to check the abort path works correctly. This issue will track progress on that. The success criterion for closing this issue is a full week of successfully running all these queries in a loop under moderate parallelization (current plan: 5 queries in flight at a time) at some scalefactor X (current plan: 5), and aborting every query (where feasible; some queries simply do not use much memory) gracefully at some higher scalefactor (current plan: 10 or at most 20).
Please pitch in if you think there is something else we should be testing, or if this plan is missing something. cc @petermattis, @cockroachdb/distsql. | 1.0 | distsql: tracking issue for continuous load tests - This is a tracking issue for the next phase of DistSQL continuous load testing. The goal is to test DistSQL more thoroughly, and eagerly raise any stability issues in DistSQL execution if there are any lurking under the hood.
#14288 was a success in identifying queries to empirically test in DistSQL, and #14295 was a success in identifying which TPC-H queries we could even run. We closed those issues as we got over the finish line for each query, getting them running in individual tests. It's time to step that up and run those queries under continuous, repetitive load on a production cluster, to see if we reveal any additional issues under stress.
The goal is to track two things:
1. That queries that we support do run repeatedly for weeks.
2. That queries that we don't support (e.g. data sets too big to be computed in-memory) fail gracefully without crashing cockroach nodes.
The cluster to be used for continuous load testing is Navy. Load will be monitored by me and @asubiotto. The load generator used will be `loadgen/tpch`.
The queries we will run are those TPC-H that were seen to work previously, namely:
* Query 1
* Query 3
* Query 7
* Query 8
* Query 9
* Query 15
* Query 19
We will initially run it on `scalefactor=5`, expecting success. We will then up the scalefactor until we abort every query due to OOM, to check the abort path works correctly. This issue will track progress on that. The success criterion for closing this issue is a full week of successfully running all these queries in a loop under moderate parallelization (current plan: 5 queries in flight at a time) at some scalefactor X (current plan: 5), and aborting every query (where feasible; some queries simply do not use much memory) gracefully at some higher scalefactor (current plan: 10 or at most 20).
Please pitch in if you think there is something else we should be testing, or if this plan is missing something. cc @petermattis, @cockroachdb/distsql. | non_defect | distsql tracking issue for continuous load tests this is a tracking issue for the next phase of distsql continuous load testing the goal is to test distsql more thoroughly and eagerly raise any stability issues in distsql execution if there are any lurking under the hood was a success in identifying queries to empirically test in distsql and was a success in identifying which tpc h queries we could even run we closed those issues as we got over the finish line for each query getting them running in individual tests it s time to step that up and run those queries under continuous repetitive load on a production cluster to see if we reveal any additional issues under stress the goal is to track two things that queries that we support do run repeatedly for weeks that queries that we don t support e g data sets too big to be computed in memory fail gracefully without crashing cockroach nodes the cluster to be used for continuous load testing is navy load will be monitored by me and asubiotto the load generator used will be loadgen tpch the queries we will run are those tpc h that were seen to work previously namely query query query query query query query we will initially run it on scalefactor expecting success we will then up the scalefactor until we abort every query due to oom to check the abort path works correctly this issue will track progress on that the success criterion for closing this issue is a full week of successfully running all these queries in a loop under moderate parallelization current plan queries in flight at a time at some scalefactor x current plan and aborting every query where feasible some queries simply do not use much memory gracefully at some higher scalefactor current plan or at most please pitch in if you think there is something else we should be testing or if this plan is missing something cc petermattis cockroachdb distsql | 0 |
8,829 | 2,612,905,157 | IssuesEvent | 2015-02-27 17:25:35 | chrsmith/windows-package-manager | https://api.github.com/repos/chrsmith/windows-package-manager | closed | Error installing Notepad++ | auto-migrated Type-Defect | ```
What steps will reproduce the problem?
1. Open Npackd 1.6
2. Search for "Notepad++"
3. Click install.
What is the expected output? What do you see instead?
Expected output: install without problems.
Instead: Error: Install/Uninstall: Process C:\WINDOWS\system32\cmd.exe exited
with the code 1
What version of the product are you using? On what operating system?
Npackd 1.6.3 under Windows Server 2003.
Please provide any additional information below.
Other software (Firefox, Flash, Eclipse, VLC) installed without problems.
```
Original issue reported on code.google.com by `cristian...@gmail.com` on 16 Dec 2011 at 12:32 | 1.0 | Error installing Notepad++ - ```
What steps will reproduce the problem?
1. Open Npackd 1.6
2. Search for "Notepad++"
3. Click install.
What is the expected output? What do you see instead?
Expected output: install without problems.
Instead: Error: Install/Uninstall: Process C:\WINDOWS\system32\cmd.exe exited
with the code 1
What version of the product are you using? On what operating system?
Npackd 1.6.3 under Windows Server 2003.
Please provide any additional information below.
Other software (Firefox, Flash, Eclipse, VLC) installed without problems.
```
Original issue reported on code.google.com by `cristian...@gmail.com` on 16 Dec 2011 at 12:32 | defect | error installing notepad what steps will reproduce the problem open npackd search for notepad click install what is the expected output what do you see instead expected output install without problems instead error install uninstall process c windows cmd exe exited with the code what version of the product are you using on what operating system npackd under windows server please provide any additional information below other software firefox flash eclipse vlc installed without problems original issue reported on code google com by cristian gmail com on dec at | 1 |
51,819 | 13,211,319,239 | IssuesEvent | 2020-08-15 22:16:54 | icecube-trac/tix4 | https://api.github.com/repos/icecube-trac/tix4 | opened | DomTools examples don't run (Trac #1119) | Incomplete Migration Migrated from Trac combo reconstruction defect | <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/1119">https://code.icecube.wisc.edu/projects/icecube/ticket/1119</a>, reported by kjmeagherand owned by olivas</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:11:57",
"_ts": "1550067117911749",
"description": "DAQReTrigger.py and I3LCCleaning-DOMLaunches.py can'l load payloads-unpacker\n/I3FirstPulsifierExample.py bad input to I3Reader\nIC80toIC40RetriggerWithSLCFilter.py can't load libDOMcalibrator\nIC80toIC60Retriggering.py can't load libtwr-decode",
"reporter": "kjmeagher",
"cc": "",
"resolution": "fixed",
"time": "2015-08-17T14:15:52",
"component": "combo reconstruction",
"summary": "DomTools examples don't run",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "olivas",
"type": "defect"
}
```
</p>
</details>
| 1.0 | DomTools examples don't run (Trac #1119) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/1119">https://code.icecube.wisc.edu/projects/icecube/ticket/1119</a>, reported by kjmeagherand owned by olivas</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:11:57",
"_ts": "1550067117911749",
"description": "DAQReTrigger.py and I3LCCleaning-DOMLaunches.py can'l load payloads-unpacker\n/I3FirstPulsifierExample.py bad input to I3Reader\nIC80toIC40RetriggerWithSLCFilter.py can't load libDOMcalibrator\nIC80toIC60Retriggering.py can't load libtwr-decode",
"reporter": "kjmeagher",
"cc": "",
"resolution": "fixed",
"time": "2015-08-17T14:15:52",
"component": "combo reconstruction",
"summary": "DomTools examples don't run",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "olivas",
"type": "defect"
}
```
</p>
</details>
| defect | domtools examples don t run trac migrated from json status closed changetime ts description daqretrigger py and domlaunches py can l load payloads unpacker n py bad input to py can t load libdomcalibrator py can t load libtwr decode reporter kjmeagher cc resolution fixed time component combo reconstruction summary domtools examples don t run priority normal keywords milestone owner olivas type defect | 1 |
50,947 | 13,187,991,082 | IssuesEvent | 2020-08-13 05:14:21 | icecube-trac/tix3 | https://api.github.com/repos/icecube-trac/tix3 | closed | trigger-sim needs specially keyed volume trigger for each instance (Trac #1717) | Migrated from Trac combo simulation defect | When running the trigger-sim segment on hitspool data younger than May 9th 2016, I get the following error:
`RuntimeError: Tray already contains module named "InIceRawdata_triggersim_cyl" of type CylinderTrigger (in I3Tray::param_setter I3Tray::AddModule(boost::python::api::object, std::string))`
Which is caused (I guess) by multiple volume trigger instances in the frame. Would be nice to have the same behaviour as we have for multiple SMTs already as well for multiple clyinder triggers.
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1717">https://code.icecube.wisc.edu/ticket/1717</a>, reported by dheereman and owned by olivas</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:12:58",
"description": "When running the trigger-sim segment on hitspool data younger than May 9th 2016, I get the following error: \n`RuntimeError: Tray already contains module named \"InIceRawdata_triggersim_cyl\" of type CylinderTrigger (in I3Tray::param_setter I3Tray::AddModule(boost::python::api::object, std::string))`\n\nWhich is caused (I guess) by multiple volume trigger instances in the frame. Would be nice to have the same behaviour as we have for multiple SMTs already as well for multiple clyinder triggers.",
"reporter": "dheereman",
"cc": "",
"resolution": "fixed",
"_ts": "1550067178841456",
"component": "combo simulation",
"summary": "trigger-sim needs specially keyed volume trigger for each instance",
"priority": "critical",
"keywords": "trigger-sim, multiple volume rigger instances",
"time": "2016-05-30T20:05:37",
"milestone": "",
"owner": "olivas",
"type": "defect"
}
```
</p>
</details>
| 1.0 | trigger-sim needs specially keyed volume trigger for each instance (Trac #1717) - When running the trigger-sim segment on hitspool data younger than May 9th 2016, I get the following error:
`RuntimeError: Tray already contains module named "InIceRawdata_triggersim_cyl" of type CylinderTrigger (in I3Tray::param_setter I3Tray::AddModule(boost::python::api::object, std::string))`
Which is caused (I guess) by multiple volume trigger instances in the frame. Would be nice to have the same behaviour as we have for multiple SMTs already as well for multiple clyinder triggers.
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1717">https://code.icecube.wisc.edu/ticket/1717</a>, reported by dheereman and owned by olivas</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:12:58",
"description": "When running the trigger-sim segment on hitspool data younger than May 9th 2016, I get the following error: \n`RuntimeError: Tray already contains module named \"InIceRawdata_triggersim_cyl\" of type CylinderTrigger (in I3Tray::param_setter I3Tray::AddModule(boost::python::api::object, std::string))`\n\nWhich is caused (I guess) by multiple volume trigger instances in the frame. Would be nice to have the same behaviour as we have for multiple SMTs already as well for multiple clyinder triggers.",
"reporter": "dheereman",
"cc": "",
"resolution": "fixed",
"_ts": "1550067178841456",
"component": "combo simulation",
"summary": "trigger-sim needs specially keyed volume trigger for each instance",
"priority": "critical",
"keywords": "trigger-sim, multiple volume rigger instances",
"time": "2016-05-30T20:05:37",
"milestone": "",
"owner": "olivas",
"type": "defect"
}
```
</p>
</details>
| defect | trigger sim needs specially keyed volume trigger for each instance trac when running the trigger sim segment on hitspool data younger than may i get the following error runtimeerror tray already contains module named inicerawdata triggersim cyl of type cylindertrigger in param setter addmodule boost python api object std string which is caused i guess by multiple volume trigger instances in the frame would be nice to have the same behaviour as we have for multiple smts already as well for multiple clyinder triggers migrated from json status closed changetime description when running the trigger sim segment on hitspool data younger than may i get the following error n runtimeerror tray already contains module named inicerawdata triggersim cyl of type cylindertrigger in param setter addmodule boost python api object std string n nwhich is caused i guess by multiple volume trigger instances in the frame would be nice to have the same behaviour as we have for multiple smts already as well for multiple clyinder triggers reporter dheereman cc resolution fixed ts component combo simulation summary trigger sim needs specially keyed volume trigger for each instance priority critical keywords trigger sim multiple volume rigger instances time milestone owner olivas type defect | 1 |
13,553 | 2,765,616,484 | IssuesEvent | 2015-04-29 21:31:51 | ljean/modbus-tk | https://api.github.com/repos/ljean/modbus-tk | closed | Server should return when it fails to run Server._do_init. | auto-migrated Priority-Medium Type-Defect | ```
When a TcpServer fails to bound to a socket (because it is already in use or
user hasn't proper permissions) the TcpServer hangs.
The TcpServer hangs because the `_do_init()` method is called within a
try/catch all statement.
try:
self._do_init()
while self._go.isSet():
self._do_run()
LOGGER.info("%s has stopped" % self.__class__)
self._do_exit()
except Exception, excpt:
LOGGER.error("server error: %s" % str(excpt))
self._make_thread() #make possible to rerun in future
I think that the call to `self_do_init()` should be done outside try/catch
block. These exception must boil up to caller.
```
Original issue reported on code.google.com by `AWooster...@gmail.com` on 28 Feb 2015 at 7:50 | 1.0 | Server should return when it fails to run Server._do_init. - ```
When a TcpServer fails to bound to a socket (because it is already in use or
user hasn't proper permissions) the TcpServer hangs.
The TcpServer hangs because the `_do_init()` method is called within a
try/catch all statement.
try:
self._do_init()
while self._go.isSet():
self._do_run()
LOGGER.info("%s has stopped" % self.__class__)
self._do_exit()
except Exception, excpt:
LOGGER.error("server error: %s" % str(excpt))
self._make_thread() #make possible to rerun in future
I think that the call to `self_do_init()` should be done outside try/catch
block. These exception must boil up to caller.
```
Original issue reported on code.google.com by `AWooster...@gmail.com` on 28 Feb 2015 at 7:50 | defect | server should return when it fails to run server do init when a tcpserver fails to bound to a socket because it is already in use or user hasn t proper permissions the tcpserver hangs the tcpserver hangs because the do init method is called within a try catch all statement try self do init while self go isset self do run logger info s has stopped self class self do exit except exception excpt logger error server error s str excpt self make thread make possible to rerun in future i think that the call to self do init should be done outside try catch block these exception must boil up to caller original issue reported on code google com by awooster gmail com on feb at | 1 |
27,531 | 5,041,015,848 | IssuesEvent | 2016-12-19 08:46:25 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | opened | Cluster member-list update operations are not ordered | Team: Core Type: Defect | Cluster member-list update operations are not ordered, new member addition and removal operations can get reordered on receiving/processing side. Also periodic member-list publish operation has no order with other member adding/removing operations. That can cause having different member lists on different members.
For example assume cluster has [A, B, C] members;
- B shuts down
- A publishes [A, B, C] with a periodic member-list publish operation
- B is removed from both A and C. Member-list seen by;
* A -> [A, C]
* C -> [A, C]
- Periodic member-list publish operation is processed by C. Member-list seen by;
* A -> [A, C]
* C -> [A, B, C]
After that point all membership updates will be rejected by C with following error (see `ClusterServiceImpl.shouldProcessMemberUpdate()`);
```
Received an inconsistent member update which contains new members
and removes some of the current members! Ignoring and requesting a new member update...
```
This issue can be fixed by adding an incremental sequence in form `(master-uuid, sequence)` to all member update operations. | 1.0 | Cluster member-list update operations are not ordered - Cluster member-list update operations are not ordered, new member addition and removal operations can get reordered on receiving/processing side. Also periodic member-list publish operation has no order with other member adding/removing operations. That can cause having different member lists on different members.
For example assume cluster has [A, B, C] members;
- B shuts down
- A publishes [A, B, C] with a periodic member-list publish operation
- B is removed from both A and C. Member-list seen by;
* A -> [A, C]
* C -> [A, C]
- Periodic member-list publish operation is processed by C. Member-list seen by;
* A -> [A, C]
* C -> [A, B, C]
After that point all membership updates will be rejected by C with following error (see `ClusterServiceImpl.shouldProcessMemberUpdate()`);
```
Received an inconsistent member update which contains new members
and removes some of the current members! Ignoring and requesting a new member update...
```
This issue can be fixed by adding an incremental sequence in form `(master-uuid, sequence)` to all member update operations. | defect | cluster member list update operations are not ordered cluster member list update operations are not ordered new member addition and removal operations can get reordered on receiving processing side also periodic member list publish operation has no order with other member adding removing operations that can cause having different member lists on different members for example assume cluster has members b shuts down a publishes with a periodic member list publish operation b is removed from both a and c member list seen by a c periodic member list publish operation is processed by c member list seen by a c after that point all membership updates will be rejected by c with following error see clusterserviceimpl shouldprocessmemberupdate received an inconsistent member update which contains new members and removes some of the current members ignoring and requesting a new member update this issue can be fixed by adding an incremental sequence in form master uuid sequence to all member update operations | 1 |
73,562 | 24,689,995,741 | IssuesEvent | 2022-10-19 07:50:13 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | opened | Hazelcast-Hibernate.PhoneHomeService thread is using one full CPU | Type: Defect | **Describe the bug**
We noticed that the `Hazelcast-Hibernate.PhoneHomeService` thread is using one full CPU all the time. The stack trace is as follows:
```
"Hazelcast-Hibernate.PhoneHomeService" #73 daemon prio=5 os_prio=0 tid=0x00007f6d7e641000 nid=0x4d runnable [0x00007f6cf4bde000]
java.lang.Thread.State: RUNNABLE
at java.util.concurrent.ScheduledThreadPoolExecutor$DelayedWorkQueue.poll(ScheduledThreadPoolExecutor.java:809)
at java.util.concurrent.ThreadPoolExecutor.getTask(ThreadPoolExecutor.java:1073)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1134)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
at java.lang.Thread.run(Thread.java:750)
```
It seems to be scheduled here: https://github.com/hazelcast/hazelcast/blob/master/hazelcast/src/main/java/com/hazelcast/internal/util/phonehome/PhoneHome.java#L97
The Java app is running on a Kubernetes cluster and the URL http://phonehome.hazelcast.com/ping is reachable from there. However, we have seen the same behavior on other systems which prevent any external communication.
As a solution we have disabled the feature as documented on https://docs.hazelcast.com/imdg/4.2/phone-homes
**Expected behavior**
The thread should not take one full CPU but should only be scheduled for a short time, no matter if the URL above is reachable or not.
**Additional context**
- Hazelcast 4.2.2, no clustering, only used in the local JVM for Hibernate 2nd level cache and Spring Cache
- Java 8
- Spring Boot 2.6.1
- Hibernate 5.6.1
- RedHat UBI micro image, Eclipse Temurin JRE
| 1.0 | Hazelcast-Hibernate.PhoneHomeService thread is using one full CPU - **Describe the bug**
We noticed that the `Hazelcast-Hibernate.PhoneHomeService` thread is using one full CPU all the time. The stack trace is as follows:
```
"Hazelcast-Hibernate.PhoneHomeService" #73 daemon prio=5 os_prio=0 tid=0x00007f6d7e641000 nid=0x4d runnable [0x00007f6cf4bde000]
java.lang.Thread.State: RUNNABLE
at java.util.concurrent.ScheduledThreadPoolExecutor$DelayedWorkQueue.poll(ScheduledThreadPoolExecutor.java:809)
at java.util.concurrent.ThreadPoolExecutor.getTask(ThreadPoolExecutor.java:1073)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1134)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
at java.lang.Thread.run(Thread.java:750)
```
It seems to be scheduled here: https://github.com/hazelcast/hazelcast/blob/master/hazelcast/src/main/java/com/hazelcast/internal/util/phonehome/PhoneHome.java#L97
The Java app is running on a Kubernetes cluster and the URL http://phonehome.hazelcast.com/ping is reachable from there. However, we have seen the same behavior on other systems which prevent any external communication.
As a solution we have disabled the feature as documented on https://docs.hazelcast.com/imdg/4.2/phone-homes
**Expected behavior**
The thread should not take one full CPU but should only be scheduled for a short time, no matter if the URL above is reachable or not.
**Additional context**
- Hazelcast 4.2.2, no clustering, only used in the local JVM for Hibernate 2nd level cache and Spring Cache
- Java 8
- Spring Boot 2.6.1
- Hibernate 5.6.1
- RedHat UBI micro image, Eclipse Temurin JRE
| defect | hazelcast hibernate phonehomeservice thread is using one full cpu describe the bug we noticed that the hazelcast hibernate phonehomeservice thread is using one full cpu all the time the stack trace is as follows hazelcast hibernate phonehomeservice daemon prio os prio tid nid runnable java lang thread state runnable at java util concurrent scheduledthreadpoolexecutor delayedworkqueue poll scheduledthreadpoolexecutor java at java util concurrent threadpoolexecutor gettask threadpoolexecutor java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java lang thread run thread java it seems to be scheduled here the java app is running on a kubernetes cluster and the url is reachable from there however we have seen the same behavior on other systems which prevent any external communication as a solution we have disabled the feature as documented on expected behavior the thread should not take one full cpu but should only be scheduled for a short time no matter if the url above is reachable or not additional context hazelcast no clustering only used in the local jvm for hibernate level cache and spring cache java spring boot hibernate redhat ubi micro image eclipse temurin jre | 1 |
6,300 | 22,740,874,056 | IssuesEvent | 2022-07-07 03:33:32 | paquesid/paques-website-automation | https://api.github.com/repos/paquesid/paques-website-automation | opened | [PDS][Data Processing] Implement Scenario Edit Scheduller | BDD Cucumber Automation | Scenario : Edit Schecduller
```
Given user login to PDS
And User click on Data Processing
And User load data to editor
And User create query using PQL
When User add scheduller
And User click on Save icon
Then Can edit scheduller query will be run automatically as scheduller
``` | 1.0 | [PDS][Data Processing] Implement Scenario Edit Scheduller - Scenario : Edit Schecduller
```
Given user login to PDS
And User click on Data Processing
And User load data to editor
And User create query using PQL
When User add scheduller
And User click on Save icon
Then Can edit scheduller query will be run automatically as scheduller
``` | non_defect | implement scenario edit scheduller scenario edit schecduller given user login to pds and user click on data processing and user load data to editor and user create query using pql when user add scheduller and user click on save icon then can edit scheduller query will be run automatically as scheduller | 0 |
496,876 | 14,357,765,475 | IssuesEvent | 2020-11-30 13:32:44 | michaelrsweet/pappl | https://api.github.com/repos/michaelrsweet/pappl | closed | When printing via the command line, vendor job options supplied via `-o` are ignored | bug priority-medium | **Describe the bug**
After having started the PostScript Printer Application as a server I try to send a print job with the following command line:
```
ps-printer-app -d test -o collate=on -o print-color-as-gray=on -o rgb-color=photo-s-rgb -o secure-printing=on -o first-digit=5 -o second-digit=6 -o third-digit=7 -o fourth-digit=8 ~/ghostscript/testfiles/CityMap.pdf
```
The options are the vendor options for this printer. I have used the same option and choice names as they show in the web interface, on the "Printer Defaults" page. The job gets printed, but with the default settings as set in the web interface.
**To Reproduce**
Run the PostScript Printer Application as server, create a printer if you have not done so, then got to the "Printer Defaults" page of the web interface. Browse through the vendor options (the ones after the resolution line). Now send a job by running the PostScript Ptrinter Application as command line utility, with a command line similar to the above, with option and choice names as you have seen them in the web interface. Observe the printout (or the debug logging) and see that the changes by the options on the command line are not applied.
**Expected behavior**
Supplying options on the command line should work.
| 1.0 | When printing via the command line, vendor job options supplied via `-o` are ignored - **Describe the bug**
After having started the PostScript Printer Application as a server I try to send a print job with the following command line:
```
ps-printer-app -d test -o collate=on -o print-color-as-gray=on -o rgb-color=photo-s-rgb -o secure-printing=on -o first-digit=5 -o second-digit=6 -o third-digit=7 -o fourth-digit=8 ~/ghostscript/testfiles/CityMap.pdf
```
The options are the vendor options for this printer. I have used the same option and choice names as they show in the web interface, on the "Printer Defaults" page. The job gets printed, but with the default settings as set in the web interface.
**To Reproduce**
Run the PostScript Printer Application as server, create a printer if you have not done so, then got to the "Printer Defaults" page of the web interface. Browse through the vendor options (the ones after the resolution line). Now send a job by running the PostScript Ptrinter Application as command line utility, with a command line similar to the above, with option and choice names as you have seen them in the web interface. Observe the printout (or the debug logging) and see that the changes by the options on the command line are not applied.
**Expected behavior**
Supplying options on the command line should work.
| non_defect | when printing via the command line vendor job options supplied via o are ignored describe the bug after having started the postscript printer application as a server i try to send a print job with the following command line ps printer app d test o collate on o print color as gray on o rgb color photo s rgb o secure printing on o first digit o second digit o third digit o fourth digit ghostscript testfiles citymap pdf the options are the vendor options for this printer i have used the same option and choice names as they show in the web interface on the printer defaults page the job gets printed but with the default settings as set in the web interface to reproduce run the postscript printer application as server create a printer if you have not done so then got to the printer defaults page of the web interface browse through the vendor options the ones after the resolution line now send a job by running the postscript ptrinter application as command line utility with a command line similar to the above with option and choice names as you have seen them in the web interface observe the printout or the debug logging and see that the changes by the options on the command line are not applied expected behavior supplying options on the command line should work | 0 |
749,237 | 26,155,053,671 | IssuesEvent | 2022-12-30 20:01:04 | azerothcore/azerothcore-wotlk | https://api.github.com/repos/azerothcore/azerothcore-wotlk | closed | Only party/raid members hear emote sounds | Invalid-Intended/WontFix/Blizzlike Confirmed ChromieCraft Generic Priority-Trivial | Original issue: https://github.com/chromiecraft/chromiecraft/issues/4372
### What client do you play on?
enUS
### Faction
Both
### Content Phase:
Generic
### Current Behaviour
Don't hear sound of emotes like /silly /flirt /train from players not in your party/raid
### Expected Blizzlike Behaviour
Hear sound of emotes like /silly /flirt /train from players not in your party/raid
### Source
- https://www.wowhead.com/item=44606/toy-train-set#comments People complaining about this toy through many expansions
- Common sense
-
### Steps to reproduce the problem
Get 2 chars at the same place
Mute sound on one of the clients
Do /train
Enjoy the silence
### Extra Notes
Tested on my local server
### AC rev. hash/commit
a2018edade7e 2022-12-29
### Operating system
Ubuntu 20.04 - Windows 10 x64
### Modules
- [mod-ah-bot](https://github.com/azerothcore/mod-ah-bot)
- [mod-bg-item-reward](https://github.com/azerothcore/mod-bg-item-reward)
- [mod-cfbg](https://github.com/azerothcore/mod-cfbg)
- [mod-chat-transmitter](https://github.com/azerothcore/mod-chat-transmitter)
- [mod-chromie-xp](https://github.com/azerothcore/mod-chromie-xp)
- [mod-cta-switch](https://github.com/azerothcore/mod-cta-switch)
- [mod-desertion-warnings](https://github.com/azerothcore/mod-desertion-warnings)
- [mod-dmf-switch](https://github.com/azerothcore/mod-dmf-switch)
- [mod-duel-reset](https://github.com/azerothcore/mod-duel-reset)
- [mod-eluna](https://github.com/azerothcore/mod-eluna)
- [mod-ip-tracker](https://github.com/azerothcore/mod-ip-tracker)
- [mod-low-level-arena](https://github.com/azerothcore/mod-low-level-arena)
- [mod-low-level-rbg](https://github.com/azerothcore/mod-low-level-rbg)
- [mod-multi-client-check](https://github.com/azerothcore/mod-multi-client-check)
- [mod-progression-system](https://github.com/azerothcore/mod-progression-system)
- [mod-pvp-titles](https://github.com/azerothcore/mod-pvp-titles)
- [mod-pvpstats-announcer](https://github.com/azerothcore/mod-pvpstats-announcer)
- [mod-queue-list-cache](https://github.com/azerothcore/mod-queue-list-cache)
- [mod-rdf-expansion](https://github.com/azerothcore/mod-rdf-expansion)
- [mod-transmog](https://github.com/azerothcore/mod-transmog)
- [mod-weekend-xp](https://github.com/azerothcore/mod-weekend-xp)
- [mod-instanced-worldbosses](https://github.com/nyeriah/mod-instanced-worldbosses)
- [lua-carbon-copy](https://github.com/55Honey/Acore_CarbonCopy)
- [lua-exchange-npc](https://github.com/55Honey/Acore_ExchangeNpc)
- [lua-custom-worldboss](https://github.com/55Honey/Acore_CustomWorldboss)
- [lua-level-up-reward](https://github.com/55Honey/Acore_LevelUpReward)
- [lua-recruit-a-friend](https://github.com/55Honey/Acore_RecruitAFriend)
- [lua-send-and-bind](https://github.com/55Honey/Acore_SendAndBind)
- [lua-temp-announcements](https://github.com/55Honey/Acore_TempAnnouncements)
- [lua-zonecheck](https://github.com/55Honey/acore_Zonecheck)
- [lua-zone-debuff](https://github.com/55Honey/Acore_ZoneDebuff)
### Customizations
None
### Server
ChromieCraft
| 1.0 | Only party/raid members hear emote sounds - Original issue: https://github.com/chromiecraft/chromiecraft/issues/4372
### What client do you play on?
enUS
### Faction
Both
### Content Phase:
Generic
### Current Behaviour
Don't hear sound of emotes like /silly /flirt /train from players not in your party/raid
### Expected Blizzlike Behaviour
Hear sound of emotes like /silly /flirt /train from players not in your party/raid
### Source
- https://www.wowhead.com/item=44606/toy-train-set#comments People complaining about this toy through many expansions
- Common sense
-
### Steps to reproduce the problem
Get 2 chars at the same place
Mute sound on one of the clients
Do /train
Enjoy the silence
### Extra Notes
Tested on my local server
### AC rev. hash/commit
a2018edade7e 2022-12-29
### Operating system
Ubuntu 20.04 - Windows 10 x64
### Modules
- [mod-ah-bot](https://github.com/azerothcore/mod-ah-bot)
- [mod-bg-item-reward](https://github.com/azerothcore/mod-bg-item-reward)
- [mod-cfbg](https://github.com/azerothcore/mod-cfbg)
- [mod-chat-transmitter](https://github.com/azerothcore/mod-chat-transmitter)
- [mod-chromie-xp](https://github.com/azerothcore/mod-chromie-xp)
- [mod-cta-switch](https://github.com/azerothcore/mod-cta-switch)
- [mod-desertion-warnings](https://github.com/azerothcore/mod-desertion-warnings)
- [mod-dmf-switch](https://github.com/azerothcore/mod-dmf-switch)
- [mod-duel-reset](https://github.com/azerothcore/mod-duel-reset)
- [mod-eluna](https://github.com/azerothcore/mod-eluna)
- [mod-ip-tracker](https://github.com/azerothcore/mod-ip-tracker)
- [mod-low-level-arena](https://github.com/azerothcore/mod-low-level-arena)
- [mod-low-level-rbg](https://github.com/azerothcore/mod-low-level-rbg)
- [mod-multi-client-check](https://github.com/azerothcore/mod-multi-client-check)
- [mod-progression-system](https://github.com/azerothcore/mod-progression-system)
- [mod-pvp-titles](https://github.com/azerothcore/mod-pvp-titles)
- [mod-pvpstats-announcer](https://github.com/azerothcore/mod-pvpstats-announcer)
- [mod-queue-list-cache](https://github.com/azerothcore/mod-queue-list-cache)
- [mod-rdf-expansion](https://github.com/azerothcore/mod-rdf-expansion)
- [mod-transmog](https://github.com/azerothcore/mod-transmog)
- [mod-weekend-xp](https://github.com/azerothcore/mod-weekend-xp)
- [mod-instanced-worldbosses](https://github.com/nyeriah/mod-instanced-worldbosses)
- [lua-carbon-copy](https://github.com/55Honey/Acore_CarbonCopy)
- [lua-exchange-npc](https://github.com/55Honey/Acore_ExchangeNpc)
- [lua-custom-worldboss](https://github.com/55Honey/Acore_CustomWorldboss)
- [lua-level-up-reward](https://github.com/55Honey/Acore_LevelUpReward)
- [lua-recruit-a-friend](https://github.com/55Honey/Acore_RecruitAFriend)
- [lua-send-and-bind](https://github.com/55Honey/Acore_SendAndBind)
- [lua-temp-announcements](https://github.com/55Honey/Acore_TempAnnouncements)
- [lua-zonecheck](https://github.com/55Honey/acore_Zonecheck)
- [lua-zone-debuff](https://github.com/55Honey/Acore_ZoneDebuff)
### Customizations
None
### Server
ChromieCraft
| non_defect | only party raid members hear emote sounds original issue what client do you play on enus faction both content phase generic current behaviour don t hear sound of emotes like silly flirt train from players not in your party raid expected blizzlike behaviour hear sound of emotes like silly flirt train from players not in your party raid source people complaining about this toy through many expansions common sense steps to reproduce the problem get chars at the same place mute sound on one of the clients do train enjoy the silence extra notes tested on my local server ac rev hash commit operating system ubuntu windows modules customizations none server chromiecraft | 0 |
72,315 | 9,565,325,251 | IssuesEvent | 2019-05-05 11:37:03 | kyma-project/community | https://api.github.com/repos/kyma-project/community | closed | Prepare an instruction on configuration settings required for a new repository | area/community area/documentation quality/content stale | **Description**
- Research what are obligatory repository settings in the kyma-project organization.
- Create an instruction for members of the organization on obligatory settings that should be defined on a new repository (e.g. only the **Squash and merge** option enabled).
- Add the instruction [here](https://github.com/kyma-project/community/tree/master/guidelines/internal-guidelines).
- Update the [README.md](https://github.com/kyma-project/community/blob/master/guidelines/internal-guidelines/README.md) with information on this new document.
**Reasons**
Consistency in the repository settings throughout the organization. You need to know not only what structure the repo should get but also what settings are required. | 1.0 | Prepare an instruction on configuration settings required for a new repository - **Description**
- Research what are obligatory repository settings in the kyma-project organization.
- Create an instruction for members of the organization on obligatory settings that should be defined on a new repository (e.g. only the **Squash and merge** option enabled).
- Add the instruction [here](https://github.com/kyma-project/community/tree/master/guidelines/internal-guidelines).
- Update the [README.md](https://github.com/kyma-project/community/blob/master/guidelines/internal-guidelines/README.md) with information on this new document.
**Reasons**
Consistency in the repository settings throughout the organization. You need to know not only what structure the repo should get but also what settings are required. | non_defect | prepare an instruction on configuration settings required for a new repository description research what are obligatory repository settings in the kyma project organization create an instruction for members of the organization on obligatory settings that should be defined on a new repository e g only the squash and merge option enabled add the instruction update the with information on this new document reasons consistency in the repository settings throughout the organization you need to know not only what structure the repo should get but also what settings are required | 0 |
713,875 | 24,542,310,804 | IssuesEvent | 2022-10-12 05:36:22 | wso2/docs-open-banking | https://api.github.com/repos/wso2/docs-open-banking | closed | [U2][OB3][Accelerator] Add util methods for different functionalities provided by DCR Validators' getRegistrationResponse method | Priority/Normal 300 Improvement | ### Affected OB version:
OB 3.0.0
### Affected OB specifications:
All
### Existing pages to be updated:
https://ob.docs.wso2.com/en/latest/develop/custom-dcr-validator/#writing-a-custom-dcr-validator
### Description (Optional):
New reusable util methods to aid adding additional attributes to the DCR response by overriding DCR Validators' getRegistrationResponse method
### Instructions:
Please update the [getRegistrationResponse method](https://ob.docs.wso2.com/en/latest/develop/custom-dcr-validator/#getregistrationresponse-method) section under [Writing a custom DCR validator](https://ob.docs.wso2.com/en/latest/develop/custom-dcr-validator/#writing-a-custom-dcr-validator
) with following details
#### getRegistrationResponse method
##### How to customize the public key retrieval from JWKS endpoint:
- If you want to append registration access token to the DCR response, you can make use of **`ValidatorUtils.generateAccessToken(clientId, tlsCert)`** method already provided.
```
public static String generateAccessToken(String clientId, String tlsCert) {
}
```
- If you want to append registration client URI to the DCR response, you can make use of already provided **`ValidatorUtils.getRegistrationClientURI()`** method
### Release date:
Sep 20, 2022
#### Release Update Levels
wso2-obiam-accelerator 3.0.0.56.full
### References:
https://github.com/wso2-enterprise/financial-open-banking/issues/7688
https://github.com/wso2-support/financial-open-banking/pull/2721
### Labels:
Type/enhancement, OB3, Accelerator
| 1.0 | [U2][OB3][Accelerator] Add util methods for different functionalities provided by DCR Validators' getRegistrationResponse method - ### Affected OB version:
OB 3.0.0
### Affected OB specifications:
All
### Existing pages to be updated:
https://ob.docs.wso2.com/en/latest/develop/custom-dcr-validator/#writing-a-custom-dcr-validator
### Description (Optional):
New reusable util methods to aid adding additional attributes to the DCR response by overriding DCR Validators' getRegistrationResponse method
### Instructions:
Please update the [getRegistrationResponse method](https://ob.docs.wso2.com/en/latest/develop/custom-dcr-validator/#getregistrationresponse-method) section under [Writing a custom DCR validator](https://ob.docs.wso2.com/en/latest/develop/custom-dcr-validator/#writing-a-custom-dcr-validator
) with following details
#### getRegistrationResponse method
##### How to customize the public key retrieval from JWKS endpoint:
- If you want to append registration access token to the DCR response, you can make use of **`ValidatorUtils.generateAccessToken(clientId, tlsCert)`** method already provided.
```
public static String generateAccessToken(String clientId, String tlsCert) {
}
```
- If you want to append registration client URI to the DCR response, you can make use of already provided **`ValidatorUtils.getRegistrationClientURI()`** method
### Release date:
Sep 20, 2022
#### Release Update Levels
wso2-obiam-accelerator 3.0.0.56.full
### References:
https://github.com/wso2-enterprise/financial-open-banking/issues/7688
https://github.com/wso2-support/financial-open-banking/pull/2721
### Labels:
Type/enhancement, OB3, Accelerator
| non_defect | add util methods for different functionalities provided by dcr validators getregistrationresponse method affected ob version ob affected ob specifications all existing pages to be updated description optional new reusable util methods to aid adding additional attributes to the dcr response by overriding dcr validators getregistrationresponse method instructions please update the section under with following details getregistrationresponse method how to customize the public key retrieval from jwks endpoint if you want to append registration access token to the dcr response you can make use of validatorutils generateaccesstoken clientid tlscert method already provided public static string generateaccesstoken string clientid string tlscert if you want to append registration client uri to the dcr response you can make use of already provided validatorutils getregistrationclienturi method release date sep release update levels obiam accelerator full references labels type enhancement accelerator | 0 |
268,247 | 28,565,873,433 | IssuesEvent | 2023-04-21 02:01:58 | vivian-r/WebGoat | https://api.github.com/repos/vivian-r/WebGoat | opened | spring-boot-starter-actuator-2.6.6.jar: 1 vulnerabilities (highest severity is: 5.5) | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-boot-starter-actuator-2.6.6.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/boot/spring-boot-actuator-autoconfigure/2.6.6/spring-boot-actuator-autoconfigure-2.6.6.jar</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (spring-boot-starter-actuator version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2023-20873](https://www.mend.io/vulnerability-database/CVE-2023-20873) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | spring-boot-actuator-autoconfigure-2.6.6.jar | Transitive | 2.6.9 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2023-20873</summary>
### Vulnerable Library - <b>spring-boot-actuator-autoconfigure-2.6.6.jar</b></p>
<p>Spring Boot Actuator AutoConfigure</p>
<p>Library home page: <a href="https://spring.io/projects/spring-boot">https://spring.io/projects/spring-boot</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/boot/spring-boot-actuator-autoconfigure/2.6.6/spring-boot-actuator-autoconfigure-2.6.6.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-actuator-2.6.6.jar (Root Library)
- :x: **spring-boot-actuator-autoconfigure-2.6.6.jar** (Vulnerable Library)
<p>Found in base branch: <b>develop</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Spring Boot versions 3.0.0 - 3.0.5, 2.7.0 - 2.7.10, and older unsupported versions, an application that is deployed to Cloud Foundry could be susceptible to a security bypass. Users of affected versions should apply the following mitigation: 3.0.x users should upgrade to 3.0.6+. 2.7.x users should upgrade to 2.7.11+. Users of older, unsupported versions should upgrade to 3.0.6+ or 2.7.11+.
<p>Publish Date: 2023-04-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-20873>CVE-2023-20873</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2023-20873">https://nvd.nist.gov/vuln/detail/CVE-2023-20873</a></p>
<p>Release Date: 2023-04-20</p>
<p>Fix Resolution (org.springframework.boot:spring-boot-actuator-autoconfigure): 3.0.6</p>
<p>Direct dependency fix Resolution (org.springframework.boot:spring-boot-starter-actuator): 2.6.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | True | spring-boot-starter-actuator-2.6.6.jar: 1 vulnerabilities (highest severity is: 5.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-boot-starter-actuator-2.6.6.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/boot/spring-boot-actuator-autoconfigure/2.6.6/spring-boot-actuator-autoconfigure-2.6.6.jar</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (spring-boot-starter-actuator version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2023-20873](https://www.mend.io/vulnerability-database/CVE-2023-20873) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | spring-boot-actuator-autoconfigure-2.6.6.jar | Transitive | 2.6.9 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2023-20873</summary>
### Vulnerable Library - <b>spring-boot-actuator-autoconfigure-2.6.6.jar</b></p>
<p>Spring Boot Actuator AutoConfigure</p>
<p>Library home page: <a href="https://spring.io/projects/spring-boot">https://spring.io/projects/spring-boot</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/boot/spring-boot-actuator-autoconfigure/2.6.6/spring-boot-actuator-autoconfigure-2.6.6.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-actuator-2.6.6.jar (Root Library)
- :x: **spring-boot-actuator-autoconfigure-2.6.6.jar** (Vulnerable Library)
<p>Found in base branch: <b>develop</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Spring Boot versions 3.0.0 - 3.0.5, 2.7.0 - 2.7.10, and older unsupported versions, an application that is deployed to Cloud Foundry could be susceptible to a security bypass. Users of affected versions should apply the following mitigation: 3.0.x users should upgrade to 3.0.6+. 2.7.x users should upgrade to 2.7.11+. Users of older, unsupported versions should upgrade to 3.0.6+ or 2.7.11+.
<p>Publish Date: 2023-04-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-20873>CVE-2023-20873</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2023-20873">https://nvd.nist.gov/vuln/detail/CVE-2023-20873</a></p>
<p>Release Date: 2023-04-20</p>
<p>Fix Resolution (org.springframework.boot:spring-boot-actuator-autoconfigure): 3.0.6</p>
<p>Direct dependency fix Resolution (org.springframework.boot:spring-boot-starter-actuator): 2.6.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | non_defect | spring boot starter actuator jar vulnerabilities highest severity is vulnerable library spring boot starter actuator jar path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework boot spring boot actuator autoconfigure spring boot actuator autoconfigure jar vulnerabilities cve severity cvss dependency type fixed in spring boot starter actuator version remediation available medium spring boot actuator autoconfigure jar transitive details cve vulnerable library spring boot actuator autoconfigure jar spring boot actuator autoconfigure library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework boot spring boot actuator autoconfigure spring boot actuator autoconfigure jar dependency hierarchy spring boot starter actuator jar root library x spring boot actuator autoconfigure jar vulnerable library found in base branch develop vulnerability details in spring boot versions and older unsupported versions an application that is deployed to cloud foundry could be susceptible to a security bypass users of affected versions should apply the following mitigation x users should upgrade to x users should upgrade to users of older unsupported versions should upgrade to or publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework boot spring boot actuator autoconfigure direct dependency fix resolution org springframework boot spring boot starter actuator step up your open source security game with mend | 0 |
396,308 | 27,112,039,770 | IssuesEvent | 2023-02-15 15:56:32 | IGNF/road2 | https://api.github.com/repos/IGNF/road2 | closed | [doc] Update administration API specification | documentation help wanted | The administration API specification was created but it must be updated :
- [ ] Update the [specifications](https://github.com/IGNF/road2/blob/develop/documentation/apis/administration/1.0.0/api.yaml) @lgrd
- [ ] Create a .md for use cases of this API @lgrd
- [ ] Review by @IGNF/road2
This spec concerns the management of services, sources and resources inside a Road2 server. | 1.0 | [doc] Update administration API specification - The administration API specification was created but it must be updated :
- [ ] Update the [specifications](https://github.com/IGNF/road2/blob/develop/documentation/apis/administration/1.0.0/api.yaml) @lgrd
- [ ] Create a .md for use cases of this API @lgrd
- [ ] Review by @IGNF/road2
This spec concerns the management of services, sources and resources inside a Road2 server. | non_defect | update administration api specification the administration api specification was created but it must be updated update the lgrd create a md for use cases of this api lgrd review by ignf this spec concerns the management of services sources and resources inside a server | 0 |
67,507 | 9,051,185,736 | IssuesEvent | 2019-02-12 10:37:28 | Glaeydar/Projekt-Car-Sharing-Management | https://api.github.com/repos/Glaeydar/Projekt-Car-Sharing-Management | opened | Anmerkungen zu Mockups durchgehen | documentation | Anmerkungen zu Mockups, die in GoogleDrive dazu geschrieben wurden, durchgehen und anpassen oder diskutieren. | 1.0 | Anmerkungen zu Mockups durchgehen - Anmerkungen zu Mockups, die in GoogleDrive dazu geschrieben wurden, durchgehen und anpassen oder diskutieren. | non_defect | anmerkungen zu mockups durchgehen anmerkungen zu mockups die in googledrive dazu geschrieben wurden durchgehen und anpassen oder diskutieren | 0 |
109,779 | 13,836,393,226 | IssuesEvent | 2020-10-14 00:55:16 | mdn/yari | https://api.github.com/repos/mdn/yari | closed | A change to header on mobile | Yari1 design system | After having a look around at home some other developer-related websites such as Github handle their headers on mobile and talking with @peterbe, we have decided to rework the header on mobile a little.
This brings it more in line with what people generally expect, and also makes the underlying implementation less fragile. Essentially this means that the initial state of the header on mobile will be:
When the menu is then expanded, it will look as below:
Here is another option for when the menu is expanded
With one of the top-level menus expanded:
## Figma Design Doc
https://www.figma.com/file/YYVJ8uqG8UFBBvQhdI7fxR/MDN-Web-Docs?node-id=221%3A7 | 1.0 | A change to header on mobile - After having a look around at home some other developer-related websites such as Github handle their headers on mobile and talking with @peterbe, we have decided to rework the header on mobile a little.
This brings it more in line with what people generally expect, and also makes the underlying implementation less fragile. Essentially this means that the initial state of the header on mobile will be:
When the menu is then expanded, it will look as below:
Here is another option for when the menu is expanded
With one of the top-level menus expanded:
## Figma Design Doc
https://www.figma.com/file/YYVJ8uqG8UFBBvQhdI7fxR/MDN-Web-Docs?node-id=221%3A7 | non_defect | a change to header on mobile after having a look around at home some other developer related websites such as github handle their headers on mobile and talking with peterbe we have decided to rework the header on mobile a little this brings it more in line with what people generally expect and also makes the underlying implementation less fragile essentially this means that the initial state of the header on mobile will be when the menu is then expanded it will look as below here is another option for when the menu is expanded with one of the top level menus expanded figma design doc | 0 |
63,349 | 12,305,724,597 | IssuesEvent | 2020-05-11 23:17:59 | alphaville/optimization-engine | https://api.github.com/repos/alphaville/optimization-engine | closed | ROS CMakefile template | codegen docs enhancement | Hi! I've been able to migrate a MHE problem that I had running on IPOPT to OpEn. So far so good, I am able to get results in less than a millisecond!
The next step should be to use the generated C code with roscpp in a ROS C++ node. Is there any template or example on how to configure the CMakefile (using cmake or cmake_simple)?
Thanks in advance! | 1.0 | ROS CMakefile template - Hi! I've been able to migrate a MHE problem that I had running on IPOPT to OpEn. So far so good, I am able to get results in less than a millisecond!
The next step should be to use the generated C code with roscpp in a ROS C++ node. Is there any template or example on how to configure the CMakefile (using cmake or cmake_simple)?
Thanks in advance! | non_defect | ros cmakefile template hi i ve been able to migrate a mhe problem that i had running on ipopt to open so far so good i am able to get results in less than a millisecond the next step should be to use the generated c code with roscpp in a ros c node is there any template or example on how to configure the cmakefile using cmake or cmake simple thanks in advance | 0 |
191,885 | 22,215,862,043 | IssuesEvent | 2022-06-08 01:31:11 | panasalap/linux-4.1.15 | https://api.github.com/repos/panasalap/linux-4.1.15 | reopened | CVE-2017-18249 (High) detected in linux-yocto-devv4.2.8 | security vulnerability | ## CVE-2017-18249 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-devv4.2.8</b></p></summary>
<p>
<p>Linux Embedded Kernel - tracks the next mainline release</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto-dev>https://git.yoctoproject.org/git/linux-yocto-dev</a></p>
<p>Found in HEAD commit: <a href="https://github.com/panasalap/linux-4.1.15/commit/aae4c2fa46027fd4c477372871df090c6b94f3f1">aae4c2fa46027fd4c477372871df090c6b94f3f1</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/f2fs/node.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/f2fs/node.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The add_free_nid function in fs/f2fs/node.c in the Linux kernel before 4.12 does not properly track an allocated nid, which allows local users to cause a denial of service (race condition) or possibly have unspecified other impact via concurrent threads.
<p>Publish Date: 2018-03-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18249>CVE-2017-18249</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-18249">https://nvd.nist.gov/vuln/detail/CVE-2017-18249</a></p>
<p>Release Date: 2018-03-26</p>
<p>Fix Resolution: 4.12</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2017-18249 (High) detected in linux-yocto-devv4.2.8 - ## CVE-2017-18249 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-devv4.2.8</b></p></summary>
<p>
<p>Linux Embedded Kernel - tracks the next mainline release</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto-dev>https://git.yoctoproject.org/git/linux-yocto-dev</a></p>
<p>Found in HEAD commit: <a href="https://github.com/panasalap/linux-4.1.15/commit/aae4c2fa46027fd4c477372871df090c6b94f3f1">aae4c2fa46027fd4c477372871df090c6b94f3f1</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/f2fs/node.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/f2fs/node.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The add_free_nid function in fs/f2fs/node.c in the Linux kernel before 4.12 does not properly track an allocated nid, which allows local users to cause a denial of service (race condition) or possibly have unspecified other impact via concurrent threads.
<p>Publish Date: 2018-03-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18249>CVE-2017-18249</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-18249">https://nvd.nist.gov/vuln/detail/CVE-2017-18249</a></p>
<p>Release Date: 2018-03-26</p>
<p>Fix Resolution: 4.12</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_defect | cve high detected in linux yocto cve high severity vulnerability vulnerable library linux yocto linux embedded kernel tracks the next mainline release library home page a href found in head commit a href found in base branch master vulnerable source files fs node c fs node c vulnerability details the add free nid function in fs node c in the linux kernel before does not properly track an allocated nid which allows local users to cause a denial of service race condition or possibly have unspecified other impact via concurrent threads publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
746,776 | 26,045,086,758 | IssuesEvent | 2022-12-22 13:45:44 | threefoldfoundation/info_manual3 | https://api.github.com/repos/threefoldfoundation/info_manual3 | closed | For Mastodon weblet, please add "what happens if I forgot to fund my mastodon server" | priority_major | We need to clarify in the manual for the mastodon weblet what happens when the person runs out of funds, based on conversation with Thabet. See https://library.threefold.me/info/manual/#/manual__grace_period?id=grace-period | 1.0 | For Mastodon weblet, please add "what happens if I forgot to fund my mastodon server" - We need to clarify in the manual for the mastodon weblet what happens when the person runs out of funds, based on conversation with Thabet. See https://library.threefold.me/info/manual/#/manual__grace_period?id=grace-period | non_defect | for mastodon weblet please add what happens if i forgot to fund my mastodon server we need to clarify in the manual for the mastodon weblet what happens when the person runs out of funds based on conversation with thabet see | 0 |
10,986 | 2,622,856,930 | IssuesEvent | 2015-03-04 08:08:18 | max99x/inline-search-chrome-ext | https://api.github.com/repos/max99x/inline-search-chrome-ext | closed | Manual-lookup frame not movable when the host page is scrolled. | auto-migrated Priority-Medium Type-Defect | ```
When doing a manual query (through the shortcut), the resulting form is
displayed in a fixed position in the center of the screen. If the containing
page is scrolled, isInsideFrame() does not calculate the frame position
correctly which makes moving the frame impossible.
```
Original issue reported on code.google.com by `max99x` on 11 Mar 2010 at 4:18 | 1.0 | Manual-lookup frame not movable when the host page is scrolled. - ```
When doing a manual query (through the shortcut), the resulting form is
displayed in a fixed position in the center of the screen. If the containing
page is scrolled, isInsideFrame() does not calculate the frame position
correctly which makes moving the frame impossible.
```
Original issue reported on code.google.com by `max99x` on 11 Mar 2010 at 4:18 | defect | manual lookup frame not movable when the host page is scrolled when doing a manual query through the shortcut the resulting form is displayed in a fixed position in the center of the screen if the containing page is scrolled isinsideframe does not calculate the frame position correctly which makes moving the frame impossible original issue reported on code google com by on mar at | 1 |
61,551 | 17,023,723,401 | IssuesEvent | 2021-07-03 03:30:00 | tomhughes/trac-tickets | https://api.github.com/repos/tomhughes/trac-tickets | closed | Nominatim does not support zip+4 addresses in the US | Component: nominatim Priority: major Resolution: fixed Type: defect | **[Submitted to the original trac issue database at 11.56am, Sunday, 19th June 2011]**
I asked this on help.openstreetmap.org first: http://help.openstreetmap.org/questions/5826/can-nominatim-handle-zip4-lookup
It would seem that Nominatim has no support for zip+4 codes in US addresses. While its understandable that it cannot return a zip+4 zip code, adding a zip+4 to an address will cause the geocoder to not match an address that it would otherwise match.
* 19 Elizabeth Street, New York, NY, 10013-4803: http://nominatim.openstreetmap.org/search?q=19%20Elizabeth%20Street%2C%20New%20York%2C%20NY%2C%2010013-4803&format=xml&polygon=1&addressdetails=1&limit=50
* 19 Elizabeth Street, New York, NY, 10013: http://nominatim.openstreetmap.org/search?q=19%20Elizabeth%20Street%2C%20New%20York%2C%20NY%2C%2010013&format=xml&polygon=1&addressdetails=1&limit=50 | 1.0 | Nominatim does not support zip+4 addresses in the US - **[Submitted to the original trac issue database at 11.56am, Sunday, 19th June 2011]**
I asked this on help.openstreetmap.org first: http://help.openstreetmap.org/questions/5826/can-nominatim-handle-zip4-lookup
It would seem that Nominatim has no support for zip+4 codes in US addresses. While its understandable that it cannot return a zip+4 zip code, adding a zip+4 to an address will cause the geocoder to not match an address that it would otherwise match.
* 19 Elizabeth Street, New York, NY, 10013-4803: http://nominatim.openstreetmap.org/search?q=19%20Elizabeth%20Street%2C%20New%20York%2C%20NY%2C%2010013-4803&format=xml&polygon=1&addressdetails=1&limit=50
* 19 Elizabeth Street, New York, NY, 10013: http://nominatim.openstreetmap.org/search?q=19%20Elizabeth%20Street%2C%20New%20York%2C%20NY%2C%2010013&format=xml&polygon=1&addressdetails=1&limit=50 | defect | nominatim does not support zip addresses in the us i asked this on help openstreetmap org first it would seem that nominatim has no support for zip codes in us addresses while its understandable that it cannot return a zip zip code adding a zip to an address will cause the geocoder to not match an address that it would otherwise match elizabeth street new york ny elizabeth street new york ny | 1 |
32,000 | 6,676,597,627 | IssuesEvent | 2017-10-05 06:47:24 | proarc/proarc | https://api.github.com/repos/proarc/proarc | closed | Povinnost vyplnění - vnitřní část periodika | auto-migrated Priority-Low Type-Defect | ```
Prosíme opravit:
1. přidat pole physical description
2. subject - přidat vlastní pole authority pro topic - může se vyplňovat
volně, ostatní podle czenas
3. subject - name chybí
4. identifier - chybí identifikátor oclc a sysno
```
Original issue reported on code.google.com by `daneck...@knav.cz` on 13 Jun 2014 at 9:55
| 1.0 | Povinnost vyplnění - vnitřní část periodika - ```
Prosíme opravit:
1. přidat pole physical description
2. subject - přidat vlastní pole authority pro topic - může se vyplňovat
volně, ostatní podle czenas
3. subject - name chybí
4. identifier - chybí identifikátor oclc a sysno
```
Original issue reported on code.google.com by `daneck...@knav.cz` on 13 Jun 2014 at 9:55
| defect | povinnost vyplnění vnitřní část periodika prosíme opravit přidat pole physical description subject přidat vlastní pole authority pro topic může se vyplňovat volně ostatní podle czenas subject name chybí identifier chybí identifikátor oclc a sysno original issue reported on code google com by daneck knav cz on jun at | 1 |
17,750 | 3,012,954,960 | IssuesEvent | 2015-07-29 04:37:14 | yawlfoundation/yawl | https://api.github.com/repos/yawlfoundation/yawl | closed | Deferred choice before role based multiple instance task cause problem | auto-migrated Component-Engine Priority-High Type-Defect | ```
What steps will reproduce the problem?
1. Load the enclosed spec
2. Complete the first task
What is the expected output? What do you see instead?
Issue Trackpoint Notice should be offered Fredo Corleone (fc) and Log
Trackpoint Order Entry should be offered to all participants of the role
role PO_Manager. But only Issue Trackpoint Notice is offered to fc.
```
Original issue reported on code.google.com by `stephan....@googlemail.com` on 23 Feb 2009 at 1:05
Attachments:
* [logging.yawl](https://storage.googleapis.com/google-code-attachments/yawl/issue-276/comment-0/logging.yawl)
* [orderfulfilment.ybkp](https://storage.googleapis.com/google-code-attachments/yawl/issue-276/comment-0/orderfulfilment.ybkp)
| 1.0 | Deferred choice before role based multiple instance task cause problem - ```
What steps will reproduce the problem?
1. Load the enclosed spec
2. Complete the first task
What is the expected output? What do you see instead?
Issue Trackpoint Notice should be offered Fredo Corleone (fc) and Log
Trackpoint Order Entry should be offered to all participants of the role
role PO_Manager. But only Issue Trackpoint Notice is offered to fc.
```
Original issue reported on code.google.com by `stephan....@googlemail.com` on 23 Feb 2009 at 1:05
Attachments:
* [logging.yawl](https://storage.googleapis.com/google-code-attachments/yawl/issue-276/comment-0/logging.yawl)
* [orderfulfilment.ybkp](https://storage.googleapis.com/google-code-attachments/yawl/issue-276/comment-0/orderfulfilment.ybkp)
| defect | deferred choice before role based multiple instance task cause problem what steps will reproduce the problem load the enclosed spec complete the first task what is the expected output what do you see instead issue trackpoint notice should be offered fredo corleone fc and log trackpoint order entry should be offered to all participants of the role role po manager but only issue trackpoint notice is offered to fc original issue reported on code google com by stephan googlemail com on feb at attachments | 1 |
75,976 | 26,190,840,304 | IssuesEvent | 2023-01-03 08:52:24 | DependencyTrack/dependency-track | https://api.github.com/repos/DependencyTrack/dependency-track | closed | Frontend OIDC Configmap doesn't get created as part of Helm Chart | defect in triage | ### Current Behavior
Part of Helm values.yaml is the frontend oidc configuration, which theoretically would get used to create the configmap with the config.json file of OIDC variables. However, the configmap isn't created.
I tried creating it manually to test out the feature, but it looks like the frontend docker image isn't making use of it.
### Steps to Reproduce
1. specify oidc values in values.yaml
2. deploy helm chart
3. confirm that oidc login option is not availabe
### Expected Behavior
1. specify oidc values in values.yaml
2. deploy helm chart, which then creates frontend configmap
3. oidc login gets enabled depending on avaibiliy of the required variablings
### Dependency-Track Version
4.6.x
### Dependency-Track Distribution
Container Image
### Database Server
PostgreSQL
### Database Server Version
_No response_
### Browser
Google Chrome
### Checklist
- [X] I have read and understand the [contributing guidelines](https://github.com/DependencyTrack/dependency-track/blob/master/CONTRIBUTING.md#filing-issues)
- [X] I have checked the [existing issues](https://github.com/DependencyTrack/dependency-track/issues) for whether this defect was already reported | 1.0 | Frontend OIDC Configmap doesn't get created as part of Helm Chart - ### Current Behavior
Part of Helm values.yaml is the frontend oidc configuration, which theoretically would get used to create the configmap with the config.json file of OIDC variables. However, the configmap isn't created.
I tried creating it manually to test out the feature, but it looks like the frontend docker image isn't making use of it.
### Steps to Reproduce
1. specify oidc values in values.yaml
2. deploy helm chart
3. confirm that oidc login option is not availabe
### Expected Behavior
1. specify oidc values in values.yaml
2. deploy helm chart, which then creates frontend configmap
3. oidc login gets enabled depending on avaibiliy of the required variablings
### Dependency-Track Version
4.6.x
### Dependency-Track Distribution
Container Image
### Database Server
PostgreSQL
### Database Server Version
_No response_
### Browser
Google Chrome
### Checklist
- [X] I have read and understand the [contributing guidelines](https://github.com/DependencyTrack/dependency-track/blob/master/CONTRIBUTING.md#filing-issues)
- [X] I have checked the [existing issues](https://github.com/DependencyTrack/dependency-track/issues) for whether this defect was already reported | defect | frontend oidc configmap doesn t get created as part of helm chart current behavior part of helm values yaml is the frontend oidc configuration which theoretically would get used to create the configmap with the config json file of oidc variables however the configmap isn t created i tried creating it manually to test out the feature but it looks like the frontend docker image isn t making use of it steps to reproduce specify oidc values in values yaml deploy helm chart confirm that oidc login option is not availabe expected behavior specify oidc values in values yaml deploy helm chart which then creates frontend configmap oidc login gets enabled depending on avaibiliy of the required variablings dependency track version x dependency track distribution container image database server postgresql database server version no response browser google chrome checklist i have read and understand the i have checked the for whether this defect was already reported | 1 |
142,896 | 21,903,159,332 | IssuesEvent | 2022-05-20 15:14:06 | sourcegraph/sourcegraph | https://api.github.com/repos/sourcegraph/sourcegraph | closed | JetBrains: Work on first iteration of design for first jobs to be done flow | needs-design team/integrations jetbrains-ide | TBA
**Existing Sourcegraph users without private code**
When I'm using a library I'm unfamiliar with, I want to see how others in the public have used this so I can understand how to use it better | 1.0 | JetBrains: Work on first iteration of design for first jobs to be done flow - TBA
**Existing Sourcegraph users without private code**
When I'm using a library I'm unfamiliar with, I want to see how others in the public have used this so I can understand how to use it better | non_defect | jetbrains work on first iteration of design for first jobs to be done flow tba existing sourcegraph users without private code when i m using a library i m unfamiliar with i want to see how others in the public have used this so i can understand how to use it better | 0 |
120,093 | 4,781,306,775 | IssuesEvent | 2016-10-28 08:54:21 | kubernetes/kubernetes | https://api.github.com/repos/kubernetes/kubernetes | opened | [k8s.io] Garbage collector [Feature:GarbageCollector] should orphan pods created by rc if delete options say so {Kubernetes e2e suite} | kind/flake priority/P2 | https://k8s-gubernator.appspot.com/build/kubernetes-jenkins/logs/kubernetes-garbagecollector-gci-feature/121/
Failed: [k8s.io] Garbage collector [Feature:GarbageCollector] should orphan pods created by rc if delete options say so {Kubernetes e2e suite}
```
/go/src/k8s.io/kubernetes/_output/dockerized/go/src/k8s.io/kubernetes/test/e2e/framework/framework.go:142
Oct 27 22:48:42.887: Couldn't delete ns: "e2e-tests-gc-qk4kk": namespace e2e-tests-gc-qk4kk was not deleted with limit: timed out waiting for the condition, pods remaining: 65, pods missing deletion timestamp: 0 (&errors.errorString{s:"namespace e2e-tests-gc-qk4kk was not deleted with limit: timed out waiting for the condition, pods remaining: 65, pods missing deletion timestamp: 0"})
/go/src/k8s.io/kubernetes/_output/dockerized/go/src/k8s.io/kubernetes/test/e2e/framework/framework.go:353
```
| 1.0 | [k8s.io] Garbage collector [Feature:GarbageCollector] should orphan pods created by rc if delete options say so {Kubernetes e2e suite} - https://k8s-gubernator.appspot.com/build/kubernetes-jenkins/logs/kubernetes-garbagecollector-gci-feature/121/
Failed: [k8s.io] Garbage collector [Feature:GarbageCollector] should orphan pods created by rc if delete options say so {Kubernetes e2e suite}
```
/go/src/k8s.io/kubernetes/_output/dockerized/go/src/k8s.io/kubernetes/test/e2e/framework/framework.go:142
Oct 27 22:48:42.887: Couldn't delete ns: "e2e-tests-gc-qk4kk": namespace e2e-tests-gc-qk4kk was not deleted with limit: timed out waiting for the condition, pods remaining: 65, pods missing deletion timestamp: 0 (&errors.errorString{s:"namespace e2e-tests-gc-qk4kk was not deleted with limit: timed out waiting for the condition, pods remaining: 65, pods missing deletion timestamp: 0"})
/go/src/k8s.io/kubernetes/_output/dockerized/go/src/k8s.io/kubernetes/test/e2e/framework/framework.go:353
```
| non_defect | garbage collector should orphan pods created by rc if delete options say so kubernetes suite failed garbage collector should orphan pods created by rc if delete options say so kubernetes suite go src io kubernetes output dockerized go src io kubernetes test framework framework go oct couldn t delete ns tests gc namespace tests gc was not deleted with limit timed out waiting for the condition pods remaining pods missing deletion timestamp errors errorstring s namespace tests gc was not deleted with limit timed out waiting for the condition pods remaining pods missing deletion timestamp go src io kubernetes output dockerized go src io kubernetes test framework framework go | 0 |
1,871 | 2,603,972,766 | IssuesEvent | 2015-02-24 19:00:40 | chrsmith/nishazi6 | https://api.github.com/repos/chrsmith/nishazi6 | opened | 沈阳阴茎长痘痘怎么办 | auto-migrated Priority-Medium Type-Defect | ```
沈阳阴茎长痘痘怎么办〓沈陽軍區政治部醫院性病〓TEL:024-3
1023308〓成立于1946年,68年專注于性傳播疾病的研究和治療。�
��于沈陽市沈河區二緯路32號。是一所與新中國同建立共輝煌�
��歷史悠久、設備精良、技術權威、專家云集,是預防、保健
、醫療、科研康復為一體的綜合性醫院。是國家首批公立甲��
�部隊醫院、全國首批醫療規范定點單位,是第四軍醫大學、�
��南大學等知名高等院校的教學醫院。曾被中國人民解放軍空
軍后勤部衛生部評為衛生工作先進單位,先后兩次榮立集體��
�等功。
```
-----
Original issue reported on code.google.com by `q964105...@gmail.com` on 4 Jun 2014 at 8:02 | 1.0 | 沈阳阴茎长痘痘怎么办 - ```
沈阳阴茎长痘痘怎么办〓沈陽軍區政治部醫院性病〓TEL:024-3
1023308〓成立于1946年,68年專注于性傳播疾病的研究和治療。�
��于沈陽市沈河區二緯路32號。是一所與新中國同建立共輝煌�
��歷史悠久、設備精良、技術權威、專家云集,是預防、保健
、醫療、科研康復為一體的綜合性醫院。是國家首批公立甲��
�部隊醫院、全國首批醫療規范定點單位,是第四軍醫大學、�
��南大學等知名高等院校的教學醫院。曾被中國人民解放軍空
軍后勤部衛生部評為衛生工作先進單位,先后兩次榮立集體��
�等功。
```
-----
Original issue reported on code.google.com by `q964105...@gmail.com` on 4 Jun 2014 at 8:02 | defect | 沈阳阴茎长痘痘怎么办 沈阳阴茎长痘痘怎么办〓沈陽軍區政治部醫院性病〓tel: 〓 , 。� �� 。是一所與新中國同建立共輝煌� ��歷史悠久、設備精良、技術權威、專家云集,是預防、保健 、醫療、科研康復為一體的綜合性醫院。是國家首批公立甲�� �部隊醫院、全國首批醫療規范定點單位,是第四軍醫大學、� ��南大學等知名高等院校的教學醫院。曾被中國人民解放軍空 軍后勤部衛生部評為衛生工作先進單位,先后兩次榮立集體�� �等功。 original issue reported on code google com by gmail com on jun at | 1 |
49,388 | 13,453,388,178 | IssuesEvent | 2020-09-09 00:48:12 | nasifimtiazohi/openmrs-module-fhir-1.20.0 | https://api.github.com/repos/nasifimtiazohi/openmrs-module-fhir-1.20.0 | opened | CVE-2020-11112 (High) detected in jackson-databind-2.9.10.1.jar | security vulnerability | ## CVE-2020-11112 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.10.1.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to vulnerable library: /openmrs-module-fhir-1.20.0/omod/target/fhir-1.20.0/lib/jackson-databind-2.9.10.1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.10.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-fhir-1.20.0/commit/af058c71e43795da6378a96dc75d1d9e6147f1a6">af058c71e43795da6378a96dc75d1d9e6147f1a6</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.proxy.provider.remoting.RmiProvider (aka apache/commons-proxy).
<p>Publish Date: 2020-03-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11112>CVE-2020-11112</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11112">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11112</a></p>
<p>Release Date: 2020-03-31</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.4,2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-11112 (High) detected in jackson-databind-2.9.10.1.jar - ## CVE-2020-11112 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.10.1.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to vulnerable library: /openmrs-module-fhir-1.20.0/omod/target/fhir-1.20.0/lib/jackson-databind-2.9.10.1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.10.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-fhir-1.20.0/commit/af058c71e43795da6378a96dc75d1d9e6147f1a6">af058c71e43795da6378a96dc75d1d9e6147f1a6</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.proxy.provider.remoting.RmiProvider (aka apache/commons-proxy).
<p>Publish Date: 2020-03-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11112>CVE-2020-11112</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11112">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11112</a></p>
<p>Release Date: 2020-03-31</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.4,2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_defect | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to vulnerable library openmrs module fhir omod target fhir lib jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache commons proxy provider remoting rmiprovider aka apache commons proxy publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with whitesource | 0 |
51,223 | 13,207,397,380 | IssuesEvent | 2020-08-14 22:57:01 | icecube-trac/tix4 | https://api.github.com/repos/icecube-trac/tix4 | opened | remove dependence on phys-services. Depend on project interfaces. (Trac #63) | Incomplete Migration Migrated from Trac defect offline-software | <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/63">https://code.icecube.wisc.edu/projects/icecube/ticket/63</a>, reported by troy</summary>
<p>
```json
{
"status": "closed",
"changetime": "2007-11-11T02:41:00",
"_ts": "1194748860000000",
"description": "phys-services is a dependency bottleneck for various problematic tools as well as a lot of interfaces that other projects depend on. No project (I believe) should be dependent on phys-services. The I3Muxer might belong in dataio. ",
"reporter": "troy",
"cc": "",
"resolution": "duplicate",
"time": "2007-06-14T01:16:05",
"component": "offline-software",
"summary": "remove dependence on phys-services. Depend on project interfaces.",
"priority": "critical",
"keywords": "",
"milestone": "",
"owner": "",
"type": "defect"
}
```
</p>
</details>
| 1.0 | remove dependence on phys-services. Depend on project interfaces. (Trac #63) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/63">https://code.icecube.wisc.edu/projects/icecube/ticket/63</a>, reported by troy</summary>
<p>
```json
{
"status": "closed",
"changetime": "2007-11-11T02:41:00",
"_ts": "1194748860000000",
"description": "phys-services is a dependency bottleneck for various problematic tools as well as a lot of interfaces that other projects depend on. No project (I believe) should be dependent on phys-services. The I3Muxer might belong in dataio. ",
"reporter": "troy",
"cc": "",
"resolution": "duplicate",
"time": "2007-06-14T01:16:05",
"component": "offline-software",
"summary": "remove dependence on phys-services. Depend on project interfaces.",
"priority": "critical",
"keywords": "",
"milestone": "",
"owner": "",
"type": "defect"
}
```
</p>
</details>
| defect | remove dependence on phys services depend on project interfaces trac migrated from json status closed changetime ts description phys services is a dependency bottleneck for various problematic tools as well as a lot of interfaces that other projects depend on no project i believe should be dependent on phys services the might belong in dataio reporter troy cc resolution duplicate time component offline software summary remove dependence on phys services depend on project interfaces priority critical keywords milestone owner type defect | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.