Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 757 | labels stringlengths 4 664 | body stringlengths 3 261k | index stringclasses 10 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 232k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
51,048 | 13,188,060,925 | IssuesEvent | 2020-08-13 05:26:29 | icecube-trac/tix3 | https://api.github.com/repos/icecube-trac/tix3 | closed | [domlauncher] PMTResponseSimulator random service parameter (Trac #1878) | Migrated from Trac combo simulation defect | Most other modules can take a random service object directly as a parameter, but PMTResponseSimulator cannot. Make that happen.
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1878">https://code.icecube.wisc.edu/ticket/1878</a>, reported by david.schultz and owned by cweaver</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:12:55",
"description": "Most other modules can take a random service object directly as a parameter, but PMTResponseSimulator cannot. Make that happen.",
"reporter": "david.schultz",
"cc": "olivas",
"resolution": "invalid",
"_ts": "1550067175956889",
"component": "combo simulation",
"summary": "[domlauncher] PMTResponseSimulator random service parameter",
"priority": "normal",
"keywords": "",
"time": "2016-10-01T15:53:09",
"milestone": "",
"owner": "cweaver",
"type": "defect"
}
```
</p>
</details>
| 1.0 | [domlauncher] PMTResponseSimulator random service parameter (Trac #1878) - Most other modules can take a random service object directly as a parameter, but PMTResponseSimulator cannot. Make that happen.
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1878">https://code.icecube.wisc.edu/ticket/1878</a>, reported by david.schultz and owned by cweaver</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:12:55",
"description": "Most other modules can take a random service object directly as a parameter, but PMTResponseSimulator cannot. Make that happen.",
"reporter": "david.schultz",
"cc": "olivas",
"resolution": "invalid",
"_ts": "1550067175956889",
"component": "combo simulation",
"summary": "[domlauncher] PMTResponseSimulator random service parameter",
"priority": "normal",
"keywords": "",
"time": "2016-10-01T15:53:09",
"milestone": "",
"owner": "cweaver",
"type": "defect"
}
```
</p>
</details>
| defect | pmtresponsesimulator random service parameter trac most other modules can take a random service object directly as a parameter but pmtresponsesimulator cannot make that happen migrated from json status closed changetime description most other modules can take a random service object directly as a parameter but pmtresponsesimulator cannot make that happen reporter david schultz cc olivas resolution invalid ts component combo simulation summary pmtresponsesimulator random service parameter priority normal keywords time milestone owner cweaver type defect | 1 |
258,157 | 22,287,291,302 | IssuesEvent | 2022-06-11 20:54:12 | Submitty/Submitty | https://api.github.com/repos/Submitty/Submitty | opened | Re-enable integration tests | Autograding Testing / Continuous Integration (CI) | PR #7913 disabled a number of integration tests as part of the move from Ubuntu 18.04 to Ubuntu 20.04 in the CI pipeline. These tests should be upgraded to function with the tools available with Ubuntu 20.04 and re-enabled eventually. The complete list of tests which were disabled is as follows:
[ ] `python_linehighlight.run_test`
[ ] `python_simple_homework.syntax_error`
[ ] `python_simple_homework.infinite_loop_too_much_output`
[ ] `tutorial_03_multipart.buggy`
[ ] `tutorial_03_multipart.buggy2`
[ ] `tutorial_08_memory_debugging.solution`
[ ] `tutorial_09_java_testing.correct`
[ ] `tutorial_09_java_testing.does_not_compile`
[ ] `tutorial_09_java_testing.buggy`
[ ] `tutorial_09_java_testing.still_buggy`
[ ] `tutorial_10_java_coverage.correct`
[ ] `tutorial_10_java_coverage.correct_no_coverage`
[ ] `tutorial_10_java_coverage.buggy_coverage`
[ ] `tutorial_10_java_coverage.buggy_no_coverage` | 1.0 | Re-enable integration tests - PR #7913 disabled a number of integration tests as part of the move from Ubuntu 18.04 to Ubuntu 20.04 in the CI pipeline. These tests should be upgraded to function with the tools available with Ubuntu 20.04 and re-enabled eventually. The complete list of tests which were disabled is as follows:
[ ] `python_linehighlight.run_test`
[ ] `python_simple_homework.syntax_error`
[ ] `python_simple_homework.infinite_loop_too_much_output`
[ ] `tutorial_03_multipart.buggy`
[ ] `tutorial_03_multipart.buggy2`
[ ] `tutorial_08_memory_debugging.solution`
[ ] `tutorial_09_java_testing.correct`
[ ] `tutorial_09_java_testing.does_not_compile`
[ ] `tutorial_09_java_testing.buggy`
[ ] `tutorial_09_java_testing.still_buggy`
[ ] `tutorial_10_java_coverage.correct`
[ ] `tutorial_10_java_coverage.correct_no_coverage`
[ ] `tutorial_10_java_coverage.buggy_coverage`
[ ] `tutorial_10_java_coverage.buggy_no_coverage` | non_defect | re enable integration tests pr disabled a number of integration tests as part of the move from ubuntu to ubuntu in the ci pipeline these tests should be upgraded to function with the tools available with ubuntu and re enabled eventually the complete list of tests which were disabled is as follows python linehighlight run test python simple homework syntax error python simple homework infinite loop too much output tutorial multipart buggy tutorial multipart tutorial memory debugging solution tutorial java testing correct tutorial java testing does not compile tutorial java testing buggy tutorial java testing still buggy tutorial java coverage correct tutorial java coverage correct no coverage tutorial java coverage buggy coverage tutorial java coverage buggy no coverage | 0 |
2,787 | 4,004,179,123 | IssuesEvent | 2016-05-12 05:44:25 | jamil2342/iskool | https://api.github.com/repos/jamil2342/iskool | closed | registration name takes space | Security issue | While registration I can take user name: jamil 2342 . Here I can take space as user name that should not be. | True | registration name takes space - While registration I can take user name: jamil 2342 . Here I can take space as user name that should not be. | non_defect | registration name takes space while registration i can take user name jamil here i can take space as user name that should not be | 0 |
965 | 2,792,422,240 | IssuesEvent | 2015-05-11 00:06:26 | golang/go | https://api.github.com/repos/golang/go | closed | all: go1.4rc performs slow | Performance | by **veenutanwar**:
<pre>issue with html & resource file work fine in 4 beta but slow in rc 4
please suggest</pre> | True | all: go1.4rc performs slow - by **veenutanwar**:
<pre>issue with html & resource file work fine in 4 beta but slow in rc 4
please suggest</pre> | non_defect | all performs slow by veenutanwar issue with html amp resource file work fine in beta but slow in rc please suggest | 0 |
34,609 | 7,457,854,037 | IssuesEvent | 2018-03-30 07:24:26 | kerdokullamae/test_koik_issued | https://api.github.com/repos/kerdokullamae/test_koik_issued | closed | KÜ seosete arv | C: AIS P: normal R: fixed T: defect | **Reported by eilika on 11 Aug 2014 12:25 UTC**
KÜ-l kuvatakse seotud isikute arvuks 1, kuid ühtegi isikut kü-ga seotud ei ole.
http://dev.raju.teepub/et/description_unit/view/?id=111702910118 | 1.0 | KÜ seosete arv - **Reported by eilika on 11 Aug 2014 12:25 UTC**
KÜ-l kuvatakse seotud isikute arvuks 1, kuid ühtegi isikut kü-ga seotud ei ole.
http://dev.raju.teepub/et/description_unit/view/?id=111702910118 | defect | kü seosete arv reported by eilika on aug utc kü l kuvatakse seotud isikute arvuks kuid ühtegi isikut kü ga seotud ei ole | 1 |
754,625 | 26,396,289,977 | IssuesEvent | 2023-01-12 19:44:40 | formkit/formkit | https://api.github.com/repos/formkit/formkit | closed | Mask input field for id or phone? | 🪄 enhancement 🟡 priority-2 | Hi there, this feature already exists?
Input form mask field for custom models? Like document Id and phone number? | 1.0 | Mask input field for id or phone? - Hi there, this feature already exists?
Input form mask field for custom models? Like document Id and phone number? | non_defect | mask input field for id or phone hi there this feature already exists input form mask field for custom models like document id and phone number | 0 |
15,743 | 2,869,008,159 | IssuesEvent | 2015-06-05 22:32:47 | dart-lang/sdk | https://api.github.com/repos/dart-lang/sdk | closed | Link to API docs for http_server is incorrect | Area-Pkg Pkg-HttpServer Priority-Medium Triaged Type-Defect | Looks like something changed.
Go to http://pub.dartlang.org/packages/http_server
Click link to API docs: https://api.dartlang.org/docs/channels/stable/latest/http_server.html
End up here: https://api.dartlang.org/apidocs/channels/stable/dartdoc-viewer/home | 1.0 | Link to API docs for http_server is incorrect - Looks like something changed.
Go to http://pub.dartlang.org/packages/http_server
Click link to API docs: https://api.dartlang.org/docs/channels/stable/latest/http_server.html
End up here: https://api.dartlang.org/apidocs/channels/stable/dartdoc-viewer/home | defect | link to api docs for http server is incorrect looks like something changed go to click link to api docs end up here | 1 |
62,271 | 17,023,886,186 | IssuesEvent | 2021-07-03 04:22:23 | tomhughes/trac-tickets | https://api.github.com/repos/tomhughes/trac-tickets | closed | Please add a tag for mountain peaks like natural=peak but as symbol. | Component: potlatch2 Priority: minor Resolution: fixed Type: defect | **[Submitted to the original trac issue database at 10.20am, Wednesday, 20th November 2013]**
Please add a tag for mountain peaks like natural=peak but as symbol. | 1.0 | Please add a tag for mountain peaks like natural=peak but as symbol. - **[Submitted to the original trac issue database at 10.20am, Wednesday, 20th November 2013]**
Please add a tag for mountain peaks like natural=peak but as symbol. | defect | please add a tag for mountain peaks like natural peak but as symbol please add a tag for mountain peaks like natural peak but as symbol | 1 |
324,301 | 27,798,968,028 | IssuesEvent | 2023-03-17 14:32:33 | nrwl/nx | https://api.github.com/repos/nrwl/nx | closed | 'ProxyZone' not found after migration from 15.1.1 to 15.8.5 | type: bug scope: testing tools scope: angular | ### Current Behavior
After running the migration to 15.8.5, a lot of our unit tests are failing with the error message: "Expected to be running in 'ProxyZone', but it was not found." It points to the loader function on TestbedHarnessEnvironment, but looking into it, the issue seems to be tied to @testing-library/angular. It seemed best to file the issue here since there are multiple libraries are involved.
There are two tests in the demo repo below to illustrate the problem. The test were run with two versions of @testing-library/angular: 10.11.0 and 13.3.0 (current latest).
### Expected Behavior
We expected our tests to continue to pass without error.
### GitHub Repo
https://github.com/smithpb/proxyzone-error
### Steps to Reproduce
1. running `nx test test-app` will return the error we've seen
### Nx Report
```shell
> NX Report complete - copy this into the issue template
Node : 18.14.0
OS : darwin x64
npm : 9.3.1
nx : 15.8.5
@nrwl/js : 15.8.5
@nrwl/jest : 15.8.5
@nrwl/linter : 15.8.5
@nrwl/workspace : 15.8.5
@nrwl/angular : 15.8.5
@nrwl/cli : 15.8.5
@nrwl/cypress : 15.8.5
@nrwl/devkit : 15.8.5
@nrwl/eslint-plugin-nx : 15.8.5
@nrwl/tao : 15.8.5
@nrwl/webpack : 15.8.5
@nrwl/nx-cloud : 15.1.1
typescript : 4.9.5
---------------------------------------
Community plugins:
@testing-library/angular : 13.3.0
```
### Failure Logs
_No response_
### Additional Information
_No response_ | 1.0 | 'ProxyZone' not found after migration from 15.1.1 to 15.8.5 - ### Current Behavior
After running the migration to 15.8.5, a lot of our unit tests are failing with the error message: "Expected to be running in 'ProxyZone', but it was not found." It points to the loader function on TestbedHarnessEnvironment, but looking into it, the issue seems to be tied to @testing-library/angular. It seemed best to file the issue here since there are multiple libraries are involved.
There are two tests in the demo repo below to illustrate the problem. The test were run with two versions of @testing-library/angular: 10.11.0 and 13.3.0 (current latest).
### Expected Behavior
We expected our tests to continue to pass without error.
### GitHub Repo
https://github.com/smithpb/proxyzone-error
### Steps to Reproduce
1. running `nx test test-app` will return the error we've seen
### Nx Report
```shell
> NX Report complete - copy this into the issue template
Node : 18.14.0
OS : darwin x64
npm : 9.3.1
nx : 15.8.5
@nrwl/js : 15.8.5
@nrwl/jest : 15.8.5
@nrwl/linter : 15.8.5
@nrwl/workspace : 15.8.5
@nrwl/angular : 15.8.5
@nrwl/cli : 15.8.5
@nrwl/cypress : 15.8.5
@nrwl/devkit : 15.8.5
@nrwl/eslint-plugin-nx : 15.8.5
@nrwl/tao : 15.8.5
@nrwl/webpack : 15.8.5
@nrwl/nx-cloud : 15.1.1
typescript : 4.9.5
---------------------------------------
Community plugins:
@testing-library/angular : 13.3.0
```
### Failure Logs
_No response_
### Additional Information
_No response_ | non_defect | proxyzone not found after migration from to current behavior after running the migration to a lot of our unit tests are failing with the error message expected to be running in proxyzone but it was not found it points to the loader function on testbedharnessenvironment but looking into it the issue seems to be tied to testing library angular it seemed best to file the issue here since there are multiple libraries are involved there are two tests in the demo repo below to illustrate the problem the test were run with two versions of testing library angular and current latest expected behavior we expected our tests to continue to pass without error github repo steps to reproduce running nx test test app will return the error we ve seen nx report shell nx report complete copy this into the issue template node os darwin npm nx nrwl js nrwl jest nrwl linter nrwl workspace nrwl angular nrwl cli nrwl cypress nrwl devkit nrwl eslint plugin nx nrwl tao nrwl webpack nrwl nx cloud typescript community plugins testing library angular failure logs no response additional information no response | 0 |
74,638 | 25,226,526,902 | IssuesEvent | 2022-11-14 16:20:58 | fecgov/fecfile-web-app | https://api.github.com/repos/fecgov/fecfile-web-app | closed | Defect: System to itemize JF Transfer regardless of amount | defect | Implementation of #486 was broken by subsequent development. This ticket is to re-code and re-test this functionality. Note that itemization logic is _not_ determined by aggregation group.
### Business Reason ###
Per FECA regulations, all Form 3X transactions on Line 12 must be itemized on Schedule A, regardless of amount. This includes JF Transfer transactions.
### Acceptance Criteria ###
**Given** one of the following transactions:
- Joint Fundraising Transfer
- PAC JF Transfer Memo
**Then** the transaction will be itemized upon saving
**and** appear on it's own line item on the *.fec file
### QA notes ###
1. In a report, make a JF Transfer transaction. (to make a later step easier, i'd recommend putting something in the memo text that you cans search for like "jf transfer test 1"
2. go to the reports list page. find the report where you added the JF Transfer and click the second green button on that row (for some reason the icons are missing)
3. you should be on a page that says "Test .FEC generation for <letters and numbers>"
4. Click "generate .fec". another button will appear, but wait about 5 seconds before pressing it
5. Click "download .fec" after about 5 seconds
6. Open the file that was just downloaded with notepad for PC or textedit for Mac. There must be a row representing the JF Transfer that was made in step 1, regardless of contribution aggregate (other transaction types show up depending on if the contribution aggregate is above $200). You can be sure the line for the transaction you made if the text at the end of the line matches the memo text you filled out in the form.
| 1.0 | Defect: System to itemize JF Transfer regardless of amount - Implementation of #486 was broken by subsequent development. This ticket is to re-code and re-test this functionality. Note that itemization logic is _not_ determined by aggregation group.
### Business Reason ###
Per FECA regulations, all Form 3X transactions on Line 12 must be itemized on Schedule A, regardless of amount. This includes JF Transfer transactions.
### Acceptance Criteria ###
**Given** one of the following transactions:
- Joint Fundraising Transfer
- PAC JF Transfer Memo
**Then** the transaction will be itemized upon saving
**and** appear on it's own line item on the *.fec file
### QA notes ###
1. In a report, make a JF Transfer transaction. (to make a later step easier, i'd recommend putting something in the memo text that you cans search for like "jf transfer test 1"
2. go to the reports list page. find the report where you added the JF Transfer and click the second green button on that row (for some reason the icons are missing)
3. you should be on a page that says "Test .FEC generation for <letters and numbers>"
4. Click "generate .fec". another button will appear, but wait about 5 seconds before pressing it
5. Click "download .fec" after about 5 seconds
6. Open the file that was just downloaded with notepad for PC or textedit for Mac. There must be a row representing the JF Transfer that was made in step 1, regardless of contribution aggregate (other transaction types show up depending on if the contribution aggregate is above $200). You can be sure the line for the transaction you made if the text at the end of the line matches the memo text you filled out in the form.
| defect | defect system to itemize jf transfer regardless of amount implementation of was broken by subsequent development this ticket is to re code and re test this functionality note that itemization logic is not determined by aggregation group business reason per feca regulations all form transactions on line must be itemized on schedule a regardless of amount this includes jf transfer transactions acceptance criteria given one of the following transactions joint fundraising transfer pac jf transfer memo then the transaction will be itemized upon saving and appear on it s own line item on the fec file qa notes in a report make a jf transfer transaction to make a later step easier i d recommend putting something in the memo text that you cans search for like jf transfer test go to the reports list page find the report where you added the jf transfer and click the second green button on that row for some reason the icons are missing you should be on a page that says test fec generation for click generate fec another button will appear but wait about seconds before pressing it click download fec after about seconds open the file that was just downloaded with notepad for pc or textedit for mac there must be a row representing the jf transfer that was made in step regardless of contribution aggregate other transaction types show up depending on if the contribution aggregate is above you can be sure the line for the transaction you made if the text at the end of the line matches the memo text you filled out in the form | 1 |
419,141 | 12,218,131,221 | IssuesEvent | 2020-05-01 18:40:31 | EduMIPS64/edumips64 | https://api.github.com/repos/EduMIPS64/edumips64 | closed | Set up a dependency upgrader bot | development-workflow priority:1 type:feature-request up-for-grabs | As per @pviotti's suggestion, we should set up a bot to keep dependencies updated.
We have dependencies both in the Gradle build file `build.gradle.kts` and in the documentation's `requirements.txt` (Python dependencies). | 1.0 | Set up a dependency upgrader bot - As per @pviotti's suggestion, we should set up a bot to keep dependencies updated.
We have dependencies both in the Gradle build file `build.gradle.kts` and in the documentation's `requirements.txt` (Python dependencies). | non_defect | set up a dependency upgrader bot as per pviotti s suggestion we should set up a bot to keep dependencies updated we have dependencies both in the gradle build file build gradle kts and in the documentation s requirements txt python dependencies | 0 |
144,821 | 19,307,409,127 | IssuesEvent | 2021-12-13 13:03:18 | jgeraigery/Java-Demo | https://api.github.com/repos/jgeraigery/Java-Demo | opened | CVE-2016-10735 (Medium) detected in bootstrap-3.3.7.min.js | security vulnerability | ## CVE-2016-10735 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.7.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.7/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.7/js/bootstrap.min.js</a></p>
<p>Path to dependency file: Java-Demo/src/main/webapp/dfi/style_bootstrap.html</p>
<p>Path to vulnerable library: /src/main/webapp/dfi/style_bootstrap.html</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.7.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/Java-Demo/commit/c6fb981b15217a4d0cfc36ccf725182fdf783ef1">c6fb981b15217a4d0cfc36ccf725182fdf783ef1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10735>CVE-2016-10735</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/issues/20184">https://github.com/twbs/bootstrap/issues/20184</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: 3.4.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.3.7","packageFilePaths":["/src/main/webapp/dfi/style_bootstrap.html"],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.3.7","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.4.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2016-10735","vulnerabilityDetails":"In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10735","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2016-10735 (Medium) detected in bootstrap-3.3.7.min.js - ## CVE-2016-10735 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.7.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.7/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.7/js/bootstrap.min.js</a></p>
<p>Path to dependency file: Java-Demo/src/main/webapp/dfi/style_bootstrap.html</p>
<p>Path to vulnerable library: /src/main/webapp/dfi/style_bootstrap.html</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.7.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/Java-Demo/commit/c6fb981b15217a4d0cfc36ccf725182fdf783ef1">c6fb981b15217a4d0cfc36ccf725182fdf783ef1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10735>CVE-2016-10735</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/issues/20184">https://github.com/twbs/bootstrap/issues/20184</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: 3.4.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.3.7","packageFilePaths":["/src/main/webapp/dfi/style_bootstrap.html"],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.3.7","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.4.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2016-10735","vulnerabilityDetails":"In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10735","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_defect | cve medium detected in bootstrap min js cve medium severity vulnerability vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to dependency file java demo src main webapp dfi style bootstrap html path to vulnerable library src main webapp dfi style bootstrap html dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap x before and x beta before beta xss is possible in the data target attribute a different vulnerability than cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree twitter bootstrap isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails in bootstrap x before and x beta before beta xss is possible in the data target attribute a different vulnerability than cve vulnerabilityurl | 0 |
79,967 | 29,803,433,283 | IssuesEvent | 2023-06-16 09:49:13 | SeleniumHQ/selenium | https://api.github.com/repos/SeleniumHQ/selenium | closed | [🐛 Bug]: Enabling new jdk-http-client leads to 'java.io.IOException: Too many open files' and ' Unable to find a free port' | C-java I-defect | ### What happened?
When enabling the new jdk-http-client client leads to leaking resources and eventually resulting in 'java.io.IOException: Too many open files' and ' Unable to find a free port' after while. This does _not_ occur if I disable 'System.setProperty("webdriver.http.factory", "jdk-http-client");', the legacy client does not exhibit this behavior (we have run it for many many hours without seeing this once). Therefore, I think the new driver has a resource leak of some type - both related to open files and due to ports.
### How can we reproduce the issue?
The easiest way to see this is to run selenium (see below for the details fo how I am running it) and enable the new client in a docker container (see below). Then go and run selenium many times. Use the command 'docker container stats' and monitor the PIDS from that command. Even when including the --init flag in docker run (do 'docker run --init ...') the PIDS grows without limit. This caused by the resource leak, leading to files not being closes (which is why we get 'java.io.IOException: Too many open files' ) and, since selenium tried to get a free port ' Unable to find a free port' due to the ports being exhausted.
```shell
I am running in Spring Boot Application in Java 17 running via Docker. I see this after about an hour of running continuously. See below for details:
1) Enabling the client
Add System.setProperty("webdriver.http.factory", "jdk-http-client"); to the main spring boot application. Also add the following to pom.xml:
<properties>
<java.version>17</java.version>
<selenium.constructs.version>4.8.3</selenium.constructs.version>
</properties>
<dependency>
<groupId>org.seleniumhq.selenium</groupId>
<artifactId>selenium-http-jdk-client</artifactId>
<version>${selenium.constructs.version}</version>
</dependency>
```
1) Client Code:
```
private List<String> getWebpageInternal(String url) {
WebDriver localWebDriver = null;
try {
Stopwatch stopWatch = Stopwatch.createUnstarted();
stopWatch.start();
localWebDriver = getWebDriver(useFastStrategy);
localWebDriver.get("about:blank");
try {
localWebDriver.manage().timeouts().pageLoadTimeout(Duration.ofMillis(waitMs));
localWebDriver.manage().timeouts().scriptTimeout(Duration.ofMillis(waitMs));
localWebDriver.manage().timeouts().implicitlyWait(Duration.ofMillis(waitMs));
getUrl(localWebDriver, url);
} catch (Exception e) {
// Still try to get the page source - some of the page might have loaded
}
// Note that waiting can take a long time, so for speed we currently put it before the call to stopwatch.stop();
stopWatch.stop();
long lengthWaited = stopWatch.elapsed(TimeUnit.MILLISECONDS);
if (lengthWaited < minWaitMs) {
Thread.sleep(minWaitMs - lengthWaited);
}
String pageSource = getPageSourceSafely(localWebDriver);
if (pageSource == null) {
throw new WebpageScraperTimeoutException("Was not able to get page source=" + url);
}
List<String> pageSources = new ArrayList<>();
pageSources.add(pageSource);
localWebDriver.quit();
return pageSources;
} catch (Exception e) {
LOGGER.error("Got error in MakeNewWebpageScraperVersion3", e);
quitSafely(localWebDriver);
throw new RuntimeException(e);
}
}
private String getPageSourceSafely(WebDriver localWebDriver) {
try {
return localWebDriver.getPageSource();
} catch (Exception e) {
return null;
}
}
private void quitSafely(WebDriver localWebDriver) {
try {
if (localWebDriver == null) {
return;
}
localWebDriver.quit();
} catch (Exception e) {
// nothing to do
LOGGER.info("Got error in quit() call of quitSafely", e);
}
}
private WebDriver getWebDriver(boolean useFastStrategy) {
ChromeDriverService service = new ChromeDriverService.Builder()
.withVerbose(false)
.withSilent(true)
.build();
return new ChromeDriver(service, getChromeOptions(useFastStrategy));
}
private ChromeOptions getChromeOptions(boolean useFastStrategy) {
ChromeOptions chromeOptions = new ChromeOptions();
if (useFastStrategy) {
chromeOptions.setPageLoadStrategy(PageLoadStrategy.EAGER); // was default (Normal) before.
}
// User agent is required because some websites will reject your request if it does not have a user agent
chromeOptions.addArguments(String.format("user-agent=%s", USER_AGENT));
chromeOptions.addArguments("--log-level=OFF");
chromeOptions.addArguments("--headless=new");
List<String> arguments = new LinkedList<>();
arguments.add("--disable-extensions");
arguments.add("--headless");
arguments.add("--disable-gpu");
arguments.add("--no-sandbox");
arguments.add("--incognito");
arguments.add("--disable-application-cache");
arguments.add("--disable-dev-shm-usage");
chromeOptions.addArguments(arguments);
return chromeOptions;
}
```
2) Docker Code:
```
ARG CHROME_VERSION=111.0.5563.64-1
ADD google-chrome.repo /etc/yum.repos.d/google-chrome.repo
RUN microdnf install -y google-chrome-stable-$CHROME_VERSION \
&& sed -i 's/"$HERE\/chrome"/"$HERE\/chrome" --no-sandbox/g' /opt/google/chrome/google-chrome
## ChromeDriver
ARG CHROME_DRIVER_VERSION=111.0.5563.64
RUN microdnf install -y unzip \
&& curl -s -o /tmp/chromedriver.zip https://chromedriver.storage.googleapis.com/$CHROME_DRIVER_VERSION/chromedriver_linux64.zip \
&& unzip /tmp/chromedriver.zip -d /opt \
&& rm /tmp/chromedriver.zip \
&& mv /opt/chromedriver /opt/chromedriver-$CHROME_DRIVER_VERSION \
&& chmod 755 /opt/chromedriver-$CHROME_DRIVER_VERSION \
&& ln -s /opt/chromedriver-$CHROME_DRIVER_VERSION /usr/bin/chromedriver
ENV CHROMEDRIVER_PORT 4444
ENV CHROMEDRIVER_WHITELISTED_IPS "127.0.0.1"
ENV CHROMEDRIVER_URL_BASE ''
EXPOSE 4444
EXPOSE 8080
EXPOSE 5005
ARG JAR_FILE=target/*.jar
COPY ${JAR_FILE} app.jar
# For Testing
ENTRYPOINT ["java","-jar", "-Xmx600m","/app.jar"]
```
```
### Relevant log output
```shell
For 'Unable to Find a Free Port':
java.lang.RuntimeException: Unable to find a free port
3/27/2023, 6:11:47 PM at org.openqa.selenium.net.PortProber.findFreePort(PortProber.java:62)
3/27/2023, 6:11:47 PM at org.openqa.selenium.remote.service.DriverService$Builder.build(DriverService.java:452)
3/27/2023, 6:11:47 PM at monolith.scraping.MakeNewWebpageScraperVersion3.getWebDriver(MakeNewWebpageScraperVersion3.java:194)
```
```
### Operating System
Catalina and Ubuntu 22.10
### Selenium version
Java 17
### What are the browser(s) and version(s) where you see this issue?
Chrome
### What are the browser driver(s) and version(s) where you see this issue?
Chromedriver
### Are you using Selenium Grid?
No | 1.0 | [🐛 Bug]: Enabling new jdk-http-client leads to 'java.io.IOException: Too many open files' and ' Unable to find a free port' - ### What happened?
When enabling the new jdk-http-client client leads to leaking resources and eventually resulting in 'java.io.IOException: Too many open files' and ' Unable to find a free port' after while. This does _not_ occur if I disable 'System.setProperty("webdriver.http.factory", "jdk-http-client");', the legacy client does not exhibit this behavior (we have run it for many many hours without seeing this once). Therefore, I think the new driver has a resource leak of some type - both related to open files and due to ports.
### How can we reproduce the issue?
The easiest way to see this is to run selenium (see below for the details fo how I am running it) and enable the new client in a docker container (see below). Then go and run selenium many times. Use the command 'docker container stats' and monitor the PIDS from that command. Even when including the --init flag in docker run (do 'docker run --init ...') the PIDS grows without limit. This caused by the resource leak, leading to files not being closes (which is why we get 'java.io.IOException: Too many open files' ) and, since selenium tried to get a free port ' Unable to find a free port' due to the ports being exhausted.
```shell
I am running in Spring Boot Application in Java 17 running via Docker. I see this after about an hour of running continuously. See below for details:
1) Enabling the client
Add System.setProperty("webdriver.http.factory", "jdk-http-client"); to the main spring boot application. Also add the following to pom.xml:
<properties>
<java.version>17</java.version>
<selenium.constructs.version>4.8.3</selenium.constructs.version>
</properties>
<dependency>
<groupId>org.seleniumhq.selenium</groupId>
<artifactId>selenium-http-jdk-client</artifactId>
<version>${selenium.constructs.version}</version>
</dependency>
```
1) Client Code:
```
private List<String> getWebpageInternal(String url) {
WebDriver localWebDriver = null;
try {
Stopwatch stopWatch = Stopwatch.createUnstarted();
stopWatch.start();
localWebDriver = getWebDriver(useFastStrategy);
localWebDriver.get("about:blank");
try {
localWebDriver.manage().timeouts().pageLoadTimeout(Duration.ofMillis(waitMs));
localWebDriver.manage().timeouts().scriptTimeout(Duration.ofMillis(waitMs));
localWebDriver.manage().timeouts().implicitlyWait(Duration.ofMillis(waitMs));
getUrl(localWebDriver, url);
} catch (Exception e) {
// Still try to get the page source - some of the page might have loaded
}
// Note that waiting can take a long time, so for speed we currently put it before the call to stopwatch.stop();
stopWatch.stop();
long lengthWaited = stopWatch.elapsed(TimeUnit.MILLISECONDS);
if (lengthWaited < minWaitMs) {
Thread.sleep(minWaitMs - lengthWaited);
}
String pageSource = getPageSourceSafely(localWebDriver);
if (pageSource == null) {
throw new WebpageScraperTimeoutException("Was not able to get page source=" + url);
}
List<String> pageSources = new ArrayList<>();
pageSources.add(pageSource);
localWebDriver.quit();
return pageSources;
} catch (Exception e) {
LOGGER.error("Got error in MakeNewWebpageScraperVersion3", e);
quitSafely(localWebDriver);
throw new RuntimeException(e);
}
}
private String getPageSourceSafely(WebDriver localWebDriver) {
try {
return localWebDriver.getPageSource();
} catch (Exception e) {
return null;
}
}
private void quitSafely(WebDriver localWebDriver) {
try {
if (localWebDriver == null) {
return;
}
localWebDriver.quit();
} catch (Exception e) {
// nothing to do
LOGGER.info("Got error in quit() call of quitSafely", e);
}
}
private WebDriver getWebDriver(boolean useFastStrategy) {
ChromeDriverService service = new ChromeDriverService.Builder()
.withVerbose(false)
.withSilent(true)
.build();
return new ChromeDriver(service, getChromeOptions(useFastStrategy));
}
private ChromeOptions getChromeOptions(boolean useFastStrategy) {
ChromeOptions chromeOptions = new ChromeOptions();
if (useFastStrategy) {
chromeOptions.setPageLoadStrategy(PageLoadStrategy.EAGER); // was default (Normal) before.
}
// User agent is required because some websites will reject your request if it does not have a user agent
chromeOptions.addArguments(String.format("user-agent=%s", USER_AGENT));
chromeOptions.addArguments("--log-level=OFF");
chromeOptions.addArguments("--headless=new");
List<String> arguments = new LinkedList<>();
arguments.add("--disable-extensions");
arguments.add("--headless");
arguments.add("--disable-gpu");
arguments.add("--no-sandbox");
arguments.add("--incognito");
arguments.add("--disable-application-cache");
arguments.add("--disable-dev-shm-usage");
chromeOptions.addArguments(arguments);
return chromeOptions;
}
```
2) Docker Code:
```
ARG CHROME_VERSION=111.0.5563.64-1
ADD google-chrome.repo /etc/yum.repos.d/google-chrome.repo
RUN microdnf install -y google-chrome-stable-$CHROME_VERSION \
&& sed -i 's/"$HERE\/chrome"/"$HERE\/chrome" --no-sandbox/g' /opt/google/chrome/google-chrome
## ChromeDriver
ARG CHROME_DRIVER_VERSION=111.0.5563.64
RUN microdnf install -y unzip \
&& curl -s -o /tmp/chromedriver.zip https://chromedriver.storage.googleapis.com/$CHROME_DRIVER_VERSION/chromedriver_linux64.zip \
&& unzip /tmp/chromedriver.zip -d /opt \
&& rm /tmp/chromedriver.zip \
&& mv /opt/chromedriver /opt/chromedriver-$CHROME_DRIVER_VERSION \
&& chmod 755 /opt/chromedriver-$CHROME_DRIVER_VERSION \
&& ln -s /opt/chromedriver-$CHROME_DRIVER_VERSION /usr/bin/chromedriver
ENV CHROMEDRIVER_PORT 4444
ENV CHROMEDRIVER_WHITELISTED_IPS "127.0.0.1"
ENV CHROMEDRIVER_URL_BASE ''
EXPOSE 4444
EXPOSE 8080
EXPOSE 5005
ARG JAR_FILE=target/*.jar
COPY ${JAR_FILE} app.jar
# For Testing
ENTRYPOINT ["java","-jar", "-Xmx600m","/app.jar"]
```
```
### Relevant log output
```shell
For 'Unable to Find a Free Port':
java.lang.RuntimeException: Unable to find a free port
3/27/2023, 6:11:47 PM at org.openqa.selenium.net.PortProber.findFreePort(PortProber.java:62)
3/27/2023, 6:11:47 PM at org.openqa.selenium.remote.service.DriverService$Builder.build(DriverService.java:452)
3/27/2023, 6:11:47 PM at monolith.scraping.MakeNewWebpageScraperVersion3.getWebDriver(MakeNewWebpageScraperVersion3.java:194)
```
```
### Operating System
Catalina and Ubuntu 22.10
### Selenium version
Java 17
### What are the browser(s) and version(s) where you see this issue?
Chrome
### What are the browser driver(s) and version(s) where you see this issue?
Chromedriver
### Are you using Selenium Grid?
No | defect | enabling new jdk http client leads to java io ioexception too many open files and unable to find a free port what happened when enabling the new jdk http client client leads to leaking resources and eventually resulting in java io ioexception too many open files and unable to find a free port after while this does not occur if i disable system setproperty webdriver http factory jdk http client the legacy client does not exhibit this behavior we have run it for many many hours without seeing this once therefore i think the new driver has a resource leak of some type both related to open files and due to ports how can we reproduce the issue the easiest way to see this is to run selenium see below for the details fo how i am running it and enable the new client in a docker container see below then go and run selenium many times use the command docker container stats and monitor the pids from that command even when including the init flag in docker run do docker run init the pids grows without limit this caused by the resource leak leading to files not being closes which is why we get java io ioexception too many open files and since selenium tried to get a free port unable to find a free port due to the ports being exhausted shell i am running in spring boot application in java running via docker i see this after about an hour of running continuously see below for details enabling the client add system setproperty webdriver http factory jdk http client to the main spring boot application also add the following to pom xml org seleniumhq selenium selenium http jdk client selenium constructs version client code private list getwebpageinternal string url webdriver localwebdriver null try stopwatch stopwatch stopwatch createunstarted stopwatch start localwebdriver getwebdriver usefaststrategy localwebdriver get about blank try localwebdriver manage timeouts pageloadtimeout duration ofmillis waitms localwebdriver manage timeouts scripttimeout duration ofmillis waitms localwebdriver manage timeouts implicitlywait duration ofmillis waitms geturl localwebdriver url catch exception e still try to get the page source some of the page might have loaded note that waiting can take a long time so for speed we currently put it before the call to stopwatch stop stopwatch stop long lengthwaited stopwatch elapsed timeunit milliseconds if lengthwaited minwaitms thread sleep minwaitms lengthwaited string pagesource getpagesourcesafely localwebdriver if pagesource null throw new webpagescrapertimeoutexception was not able to get page source url list pagesources new arraylist pagesources add pagesource localwebdriver quit return pagesources catch exception e logger error got error in e quitsafely localwebdriver throw new runtimeexception e private string getpagesourcesafely webdriver localwebdriver try return localwebdriver getpagesource catch exception e return null private void quitsafely webdriver localwebdriver try if localwebdriver null return localwebdriver quit catch exception e nothing to do logger info got error in quit call of quitsafely e private webdriver getwebdriver boolean usefaststrategy chromedriverservice service new chromedriverservice builder withverbose false withsilent true build return new chromedriver service getchromeoptions usefaststrategy private chromeoptions getchromeoptions boolean usefaststrategy chromeoptions chromeoptions new chromeoptions if usefaststrategy chromeoptions setpageloadstrategy pageloadstrategy eager was default normal before user agent is required because some websites will reject your request if it does not have a user agent chromeoptions addarguments string format user agent s user agent chromeoptions addarguments log level off chromeoptions addarguments headless new list arguments new linkedlist arguments add disable extensions arguments add headless arguments add disable gpu arguments add no sandbox arguments add incognito arguments add disable application cache arguments add disable dev shm usage chromeoptions addarguments arguments return chromeoptions docker code arg chrome version add google chrome repo etc yum repos d google chrome repo run microdnf install y google chrome stable chrome version sed i s here chrome here chrome no sandbox g opt google chrome google chrome chromedriver arg chrome driver version run microdnf install y unzip curl s o tmp chromedriver zip unzip tmp chromedriver zip d opt rm tmp chromedriver zip mv opt chromedriver opt chromedriver chrome driver version chmod opt chromedriver chrome driver version ln s opt chromedriver chrome driver version usr bin chromedriver env chromedriver port env chromedriver whitelisted ips env chromedriver url base expose expose expose arg jar file target jar copy jar file app jar for testing entrypoint relevant log output shell for unable to find a free port java lang runtimeexception unable to find a free port pm at org openqa selenium net portprober findfreeport portprober java pm at org openqa selenium remote service driverservice builder build driverservice java pm at monolith scraping getwebdriver java operating system catalina and ubuntu selenium version java what are the browser s and version s where you see this issue chrome what are the browser driver s and version s where you see this issue chromedriver are you using selenium grid no | 1 |
34,648 | 7,458,396,491 | IssuesEvent | 2018-03-30 10:05:25 | kerdokullamae/test_koik_issued | https://api.github.com/repos/kerdokullamae/test_koik_issued | closed | Luua AIS2 kasutajaliidese peitmise lahendus | C: AVAR P: highest R: fixed T: defect | **Reported by rainer nagel on 5 Dec 2014 14:26 UTC**
'''Object'''
Uus AIS
'''!ToDo'''
Muuta kogu AIS-i funktsionaalsus, mis ei ole vajalik crowdsourcingu portaali opereerimiseks ja PURL-de ning RDF-de genereerimiseks, nähtamatuks.
!ToDo- Sven aitab täpsustada, mis kohad tuleb ära peita.
| 1.0 | Luua AIS2 kasutajaliidese peitmise lahendus - **Reported by rainer nagel on 5 Dec 2014 14:26 UTC**
'''Object'''
Uus AIS
'''!ToDo'''
Muuta kogu AIS-i funktsionaalsus, mis ei ole vajalik crowdsourcingu portaali opereerimiseks ja PURL-de ning RDF-de genereerimiseks, nähtamatuks.
!ToDo- Sven aitab täpsustada, mis kohad tuleb ära peita.
| defect | luua kasutajaliidese peitmise lahendus reported by rainer nagel on dec utc object uus ais todo muuta kogu ais i funktsionaalsus mis ei ole vajalik crowdsourcingu portaali opereerimiseks ja purl de ning rdf de genereerimiseks nähtamatuks todo sven aitab täpsustada mis kohad tuleb ära peita | 1 |
154,088 | 12,192,599,656 | IssuesEvent | 2020-04-29 13:12:31 | kwk/test-llvm-bz-import-5 | https://api.github.com/repos/kwk/test-llvm-bz-import-5 | opened | Make MultiSource/Applications/sqlite3/speedtest.tcl portable. | BZ-BUG-STATUS: CONFIRMED Test Suite/Programs Tests dummy import from bugzilla | This issue was imported from Bugzilla https://bugs.llvm.org/show_bug.cgi?id=7871. | 2.0 | Make MultiSource/Applications/sqlite3/speedtest.tcl portable. - This issue was imported from Bugzilla https://bugs.llvm.org/show_bug.cgi?id=7871. | non_defect | make multisource applications speedtest tcl portable this issue was imported from bugzilla | 0 |
330,630 | 28,455,875,551 | IssuesEvent | 2023-04-17 07:01:31 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | closed | Fix norms_and_other_numbers.test_numpy_slogdet | NumPy Frontend Sub Task Failing Test | | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/4698303431/jobs/8330433790" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/4677318237/jobs/8284679423" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/4698303431/jobs/8330432081" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/4677318237/jobs/8284679423" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
<details>
<summary>FAILED ivy_tests/test_ivy/test_frontends/test_numpy/test_linear_algebra/test_norms_and_other_numbers.py::test_numpy_slogdet[cpu-ivy.functional.backends.jax-False-False]</summary>
2023-04-12T11:05:22.0397027Z E ValueError: setting an array element with a sequence.2023-04-12T11:05:22.0397337Z E Falsifying example: test_numpy_slogdet(2023-04-12T11:05:22.0397721Z E dtype_and_x=(['float64'], [array([[2.]])]),2023-04-12T11:05:22.0398141Z E fn_tree='ivy.functional.frontends.numpy.linalg.slogdet',2023-04-12T11:05:22.0398505Z E test_flags=FrontendFunctionTestFlags(2023-04-12T11:05:22.0398784Z E num_positional_args=0,2023-04-12T11:05:22.0399024Z E with_out=False,2023-04-12T11:05:22.0399260Z E inplace=False,2023-04-12T11:05:22.0399492Z E as_variable=[False],2023-04-12T11:05:22.0399734Z E native_arrays=[False],2023-04-12T11:05:22.0400002Z E generate_frontend_arrays=True,2023-04-12T11:05:22.0400240Z E ),2023-04-12T11:05:22.0400484Z E frontend='numpy',2023-04-12T11:05:22.0400747Z E on_device='cpu',2023-04-12T11:05:22.0400956Z E )2023-04-12T11:05:22.0401135Z E 2023-04-12T11:05:22.0401656Z E You can reproduce this example by temporarily adding @reproduce_failure('6.71.0', b'AXicY2BAACYgZgQAABwABA==') as a decorator on your test case
</details>
<details>
<summary>FAILED ivy_tests/test_ivy/test_frontends/test_numpy/test_linear_algebra/test_norms_and_other_numbers.py::test_numpy_slogdet[cpu-ivy.functional.backends.jax-False-False]</summary>
2023-04-12T11:05:22.0397027Z E ValueError: setting an array element with a sequence.2023-04-12T11:05:22.0397337Z E Falsifying example: test_numpy_slogdet(2023-04-12T11:05:22.0397721Z E dtype_and_x=(['float64'], [array([[2.]])]),2023-04-12T11:05:22.0398141Z E fn_tree='ivy.functional.frontends.numpy.linalg.slogdet',2023-04-12T11:05:22.0398505Z E test_flags=FrontendFunctionTestFlags(2023-04-12T11:05:22.0398784Z E num_positional_args=0,2023-04-12T11:05:22.0399024Z E with_out=False,2023-04-12T11:05:22.0399260Z E inplace=False,2023-04-12T11:05:22.0399492Z E as_variable=[False],2023-04-12T11:05:22.0399734Z E native_arrays=[False],2023-04-12T11:05:22.0400002Z E generate_frontend_arrays=True,2023-04-12T11:05:22.0400240Z E ),2023-04-12T11:05:22.0400484Z E frontend='numpy',2023-04-12T11:05:22.0400747Z E on_device='cpu',2023-04-12T11:05:22.0400956Z E )2023-04-12T11:05:22.0401135Z E 2023-04-12T11:05:22.0401656Z E You can reproduce this example by temporarily adding @reproduce_failure('6.71.0', b'AXicY2BAACYgZgQAABwABA==') as a decorator on your test case
</details>
| 1.0 | Fix norms_and_other_numbers.test_numpy_slogdet - | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/4698303431/jobs/8330433790" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/4677318237/jobs/8284679423" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/4698303431/jobs/8330432081" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/4677318237/jobs/8284679423" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
<details>
<summary>FAILED ivy_tests/test_ivy/test_frontends/test_numpy/test_linear_algebra/test_norms_and_other_numbers.py::test_numpy_slogdet[cpu-ivy.functional.backends.jax-False-False]</summary>
2023-04-12T11:05:22.0397027Z E ValueError: setting an array element with a sequence.2023-04-12T11:05:22.0397337Z E Falsifying example: test_numpy_slogdet(2023-04-12T11:05:22.0397721Z E dtype_and_x=(['float64'], [array([[2.]])]),2023-04-12T11:05:22.0398141Z E fn_tree='ivy.functional.frontends.numpy.linalg.slogdet',2023-04-12T11:05:22.0398505Z E test_flags=FrontendFunctionTestFlags(2023-04-12T11:05:22.0398784Z E num_positional_args=0,2023-04-12T11:05:22.0399024Z E with_out=False,2023-04-12T11:05:22.0399260Z E inplace=False,2023-04-12T11:05:22.0399492Z E as_variable=[False],2023-04-12T11:05:22.0399734Z E native_arrays=[False],2023-04-12T11:05:22.0400002Z E generate_frontend_arrays=True,2023-04-12T11:05:22.0400240Z E ),2023-04-12T11:05:22.0400484Z E frontend='numpy',2023-04-12T11:05:22.0400747Z E on_device='cpu',2023-04-12T11:05:22.0400956Z E )2023-04-12T11:05:22.0401135Z E 2023-04-12T11:05:22.0401656Z E You can reproduce this example by temporarily adding @reproduce_failure('6.71.0', b'AXicY2BAACYgZgQAABwABA==') as a decorator on your test case
</details>
<details>
<summary>FAILED ivy_tests/test_ivy/test_frontends/test_numpy/test_linear_algebra/test_norms_and_other_numbers.py::test_numpy_slogdet[cpu-ivy.functional.backends.jax-False-False]</summary>
2023-04-12T11:05:22.0397027Z E ValueError: setting an array element with a sequence.2023-04-12T11:05:22.0397337Z E Falsifying example: test_numpy_slogdet(2023-04-12T11:05:22.0397721Z E dtype_and_x=(['float64'], [array([[2.]])]),2023-04-12T11:05:22.0398141Z E fn_tree='ivy.functional.frontends.numpy.linalg.slogdet',2023-04-12T11:05:22.0398505Z E test_flags=FrontendFunctionTestFlags(2023-04-12T11:05:22.0398784Z E num_positional_args=0,2023-04-12T11:05:22.0399024Z E with_out=False,2023-04-12T11:05:22.0399260Z E inplace=False,2023-04-12T11:05:22.0399492Z E as_variable=[False],2023-04-12T11:05:22.0399734Z E native_arrays=[False],2023-04-12T11:05:22.0400002Z E generate_frontend_arrays=True,2023-04-12T11:05:22.0400240Z E ),2023-04-12T11:05:22.0400484Z E frontend='numpy',2023-04-12T11:05:22.0400747Z E on_device='cpu',2023-04-12T11:05:22.0400956Z E )2023-04-12T11:05:22.0401135Z E 2023-04-12T11:05:22.0401656Z E You can reproduce this example by temporarily adding @reproduce_failure('6.71.0', b'AXicY2BAACYgZgQAABwABA==') as a decorator on your test case
</details>
| non_defect | fix norms and other numbers test numpy slogdet tensorflow img src torch img src numpy img src jax img src failed ivy tests test ivy test frontends test numpy test linear algebra test norms and other numbers py test numpy slogdet e valueerror setting an array element with a sequence e falsifying example test numpy slogdet e dtype and x e fn tree ivy functional frontends numpy linalg slogdet e test flags frontendfunctiontestflags e num positional args e with out false e inplace false e as variable e native arrays e generate frontend arrays true e e frontend numpy e on device cpu e e e you can reproduce this example by temporarily adding reproduce failure b as a decorator on your test case failed ivy tests test ivy test frontends test numpy test linear algebra test norms and other numbers py test numpy slogdet e valueerror setting an array element with a sequence e falsifying example test numpy slogdet e dtype and x e fn tree ivy functional frontends numpy linalg slogdet e test flags frontendfunctiontestflags e num positional args e with out false e inplace false e as variable e native arrays e generate frontend arrays true e e frontend numpy e on device cpu e e e you can reproduce this example by temporarily adding reproduce failure b as a decorator on your test case | 0 |
51,273 | 13,635,088,122 | IssuesEvent | 2020-09-25 01:51:26 | nasifimtiazohi/openmrs-module-uilibrary-2.0.6 | https://api.github.com/repos/nasifimtiazohi/openmrs-module-uilibrary-2.0.6 | opened | CVE-2020-11023 (Medium) detected in jquery-1.7.2.min.js | security vulnerability | ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.7.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js</a></p>
<p>Path to vulnerable library: openmrs-module-uilibrary-2.0.6/omod/src/main/webapp/resources/scripts/jquery-1.7.2.min.js,openmrs-module-uilibrary-2.0.6/omod/target/uilibrary-2.0.6/web/module/resources/scripts/jquery-1.7.2.min.js,openmrs-module-uilibrary-2.0.6/omod/target/classes/web/module/resources/scripts/jquery-1.7.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.7.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-uilibrary-2.0.6/commit/18688ae033dc5e54e9a324ec3168b0b30ff5afc2">18688ae033dc5e54e9a324ec3168b0b30ff5afc2</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-11023 (Medium) detected in jquery-1.7.2.min.js - ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.7.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js</a></p>
<p>Path to vulnerable library: openmrs-module-uilibrary-2.0.6/omod/src/main/webapp/resources/scripts/jquery-1.7.2.min.js,openmrs-module-uilibrary-2.0.6/omod/target/uilibrary-2.0.6/web/module/resources/scripts/jquery-1.7.2.min.js,openmrs-module-uilibrary-2.0.6/omod/target/classes/web/module/resources/scripts/jquery-1.7.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.7.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-uilibrary-2.0.6/commit/18688ae033dc5e54e9a324ec3168b0b30ff5afc2">18688ae033dc5e54e9a324ec3168b0b30ff5afc2</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_defect | cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to vulnerable library openmrs module uilibrary omod src main webapp resources scripts jquery min js openmrs module uilibrary omod target uilibrary web module resources scripts jquery min js openmrs module uilibrary omod target classes web module resources scripts jquery min js dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch master vulnerability details in jquery versions greater than or equal to and before passing html containing elements from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource | 0 |
17,363 | 3,001,767,754 | IssuesEvent | 2015-07-24 13:38:27 | contao/core | https://api.github.com/repos/contao/core | closed | Fatal error in install.php after installing contao 3.5.1 via git | defect | Hei,
I just wanted to install the new 3.5.1 release via git. I cloned the repo, I ran composer install and wanted to run the install tool. I just get an Fatal Error
```
Fatal error: Class 'Database\' not found in C:\development\wamp\www\contao351\system\modules\core\library\Contao\Database.php on line 165
```
Win 8.1 / Wamp with PHP 5.5.12. | 1.0 | Fatal error in install.php after installing contao 3.5.1 via git - Hei,
I just wanted to install the new 3.5.1 release via git. I cloned the repo, I ran composer install and wanted to run the install tool. I just get an Fatal Error
```
Fatal error: Class 'Database\' not found in C:\development\wamp\www\contao351\system\modules\core\library\Contao\Database.php on line 165
```
Win 8.1 / Wamp with PHP 5.5.12. | defect | fatal error in install php after installing contao via git hei i just wanted to install the new release via git i cloned the repo i ran composer install and wanted to run the install tool i just get an fatal error fatal error class database not found in c development wamp www system modules core library contao database php on line win wamp with php | 1 |
64,448 | 18,677,772,750 | IssuesEvent | 2021-10-31 21:09:17 | unascribed/Fabrication | https://api.github.com/repos/unascribed/Fabrication | opened | [Déjà Void] only works if you jumped from a full block and it can kill you in creative | k: Defect n: Fabric s: New | Hi, I've included your mod in my Modpack Sky FABRICation 2.
I would like to use the Feature Déjà Void, but it does not work if a player falls from a slab or any other not full sized block.
And the feature can kill you in creative. I think this is not intended.
I hope you can improve the feature. Despite the problems, I would like to use the function. It would be a lot better than my KubeJS script. | 1.0 | [Déjà Void] only works if you jumped from a full block and it can kill you in creative - Hi, I've included your mod in my Modpack Sky FABRICation 2.
I would like to use the Feature Déjà Void, but it does not work if a player falls from a slab or any other not full sized block.
And the feature can kill you in creative. I think this is not intended.
I hope you can improve the feature. Despite the problems, I would like to use the function. It would be a lot better than my KubeJS script. | defect | only works if you jumped from a full block and it can kill you in creative hi i ve included your mod in my modpack sky fabrication i would like to use the feature déjà void but it does not work if a player falls from a slab or any other not full sized block and the feature can kill you in creative i think this is not intended i hope you can improve the feature despite the problems i would like to use the function it would be a lot better than my kubejs script | 1 |
374,780 | 26,131,777,515 | IssuesEvent | 2022-12-29 06:28:38 | yugabyte/yugabyte-db | https://api.github.com/repos/yugabyte/yugabyte-db | opened | [Docs] Search+Bind example does not contain search attribute | area/documentation | ### Description
In this page: [Search+Bind example](https://docs.yugabyte.com/preview/secure/authentication/ldap-authentication-ysql/#example)
the example mentioned in step 1:
`--ysql_hba_conf_csv='host all yugabyte 127.0.0.1/0 password,"host all all 0.0.0.0/0 ldap ldapserver=ldap.forumsys.com ldapprefix=""uid="" ldapsuffix="", dc=example, dc=com"" ldapport=389"'`
does not contain `ldapsearchfilter` or `ldapsearchattribute` in the example. We should add one of the two attributes the example. | 1.0 | [Docs] Search+Bind example does not contain search attribute - ### Description
In this page: [Search+Bind example](https://docs.yugabyte.com/preview/secure/authentication/ldap-authentication-ysql/#example)
the example mentioned in step 1:
`--ysql_hba_conf_csv='host all yugabyte 127.0.0.1/0 password,"host all all 0.0.0.0/0 ldap ldapserver=ldap.forumsys.com ldapprefix=""uid="" ldapsuffix="", dc=example, dc=com"" ldapport=389"'`
does not contain `ldapsearchfilter` or `ldapsearchattribute` in the example. We should add one of the two attributes the example. | non_defect | search bind example does not contain search attribute description in this page the example mentioned in step ysql hba conf csv host all yugabyte password host all all ldap ldapserver ldap forumsys com ldapprefix uid ldapsuffix dc example dc com ldapport does not contain ldapsearchfilter or ldapsearchattribute in the example we should add one of the two attributes the example | 0 |
76,434 | 26,423,745,643 | IssuesEvent | 2023-01-14 00:10:19 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | opened | Staging fails to load room content with Firefox Private Browsing | T-Defect | ### Steps to reproduce
1. Open staging.element.io in Firefox Private Browsing
2. Log in using SSO and verify the session
3. Click a room that is already open in the sidebar
The "Welcome to Element" screen stays open and the room is not displayed and I get these errors in the Browser Console:
```
Error handling m.room_key_event: QuotaExceededError: The quota has been exceeded. vendors~init.js:2:2569493
r https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
methodFactory https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
onRoomKeyEvent https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
Error uploading one-time keys v@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:1675384
storeAccount@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:1674918
storeAccount@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:865916
storeAccount@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:2743536
generateOneTimeKeys/</<@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:2745037
getAccount/<@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:2743475
getAccount@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:1674881
getAccount@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:865869
getAccount@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:2743398
generateOneTimeKeys/<@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:2744986
doTxn@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:1675209
doTxn@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:868289
generateOneTimeKeys@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:2744938
r@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:539083
maybeUploadOneTimeKeys/<@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:539925
Uncaught (in promise) DOMException: The quota has been exceeded. vendors~element-web-app.js:2
```
6. Keep trying to switch between rooms and the same thing keeps happening
7. Reload the tab and the same behaviour happens
8. Shift+Reload the tab and I am presented with the Unsupported Browser page and the Browser Console shows these errors about localstorage:
```
/sync error ConnectionError: fetch failed: NetworkError when attempting to fetch resource. vendors~init.js:2:2569493
r https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
methodFactory https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
onSyncError https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
doSync https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
sync https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
startClient https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
start https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
ue https://staging.element.io/bundles/51733431847a348f8b7e/vendors~element-web-app.js:2
ie https://staging.element.io/bundles/51733431847a348f8b7e/vendors~element-web-app.js:2
ee https://staging.element.io/bundles/51733431847a348f8b7e/vendors~element-web-app.js:2
K https://staging.element.io/bundles/51733431847a348f8b7e/vendors~element-web-app.js:2
loadSession https://staging.element.io/bundles/51733431847a348f8b7e/vendors~element-web-app.js:2
(Async: promise callback)
loadSession https://staging.element.io/bundles/51733431847a348f8b7e/vendors~element-web-app.js:2
Ke https://staging.element.io/bundles/51733431847a348f8b7e/vendors~element-web-app.js:2
(Async: promise callback)
Ke https://staging.element.io/bundles/51733431847a348f8b7e/vendors~element-web-app.js:2
yo https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
Va https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
Ws https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
Ol https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
Dl https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
Fl https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
vl https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
ml https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
ec https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
ac https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
El https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
ac https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
render https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
ne https://staging.element.io/bundles/51733431847a348f8b7e/init.js:1
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
s https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
Browser missing feature: 'localstorage' bundle.js:2:6903
methodFactory https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
s https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
s https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
Failed to open log database: InvalidStateError vendors~init.js:2:2569493
r https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
methodFactory https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
onerror https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
(Async: EventHandlerNonNull)
connect https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
connect https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
h https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
X https://staging.element.io/bundles/51733431847a348f8b7e/init.js:1
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
s https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
Uncaught (in promise) Error: Failed to open log database: InvalidStateError
onerror https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
connect https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
connect https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
h https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
X https://staging.element.io/bundles/51733431847a348f8b7e/init.js:1
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
async* https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
s https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
Browser is missing required features. vendors~init.js:2:2569493
r https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
methodFactory https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
s https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
```
Closing the Private Browsing window and trying again eventually fixes it, although I can keep reloading the page and eventually get the Unsupported Browser page. It works intermittently, maybe about half the time in my initial testing.
### Outcome
#### What did you expect?
Room content should load in Private Browsing mode
#### What happened instead?
Room content fails to load, all I see is the Welcome screen:

If I reload the page I eventually get an Unsupported Browser prompt.

### Operating system
OpenSUSE Tumbleweed 20230111 (Linux)
### Browser information
Firefox 108.0.2
### URL for webapp
staging.element.io
### Application version
Element version: 1.11.18-rc.3, Olm version: 3.2.12
### Homeserver
element.io
### Will you send logs?
No | 1.0 | Staging fails to load room content with Firefox Private Browsing - ### Steps to reproduce
1. Open staging.element.io in Firefox Private Browsing
2. Log in using SSO and verify the session
3. Click a room that is already open in the sidebar
The "Welcome to Element" screen stays open and the room is not displayed and I get these errors in the Browser Console:
```
Error handling m.room_key_event: QuotaExceededError: The quota has been exceeded. vendors~init.js:2:2569493
r https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
methodFactory https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
onRoomKeyEvent https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
Error uploading one-time keys v@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:1675384
storeAccount@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:1674918
storeAccount@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:865916
storeAccount@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:2743536
generateOneTimeKeys/</<@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:2745037
getAccount/<@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:2743475
getAccount@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:1674881
getAccount@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:865869
getAccount@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:2743398
generateOneTimeKeys/<@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:2744986
doTxn@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:1675209
doTxn@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:868289
generateOneTimeKeys@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:2744938
r@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:539083
maybeUploadOneTimeKeys/<@https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2:539925
Uncaught (in promise) DOMException: The quota has been exceeded. vendors~element-web-app.js:2
```
6. Keep trying to switch between rooms and the same thing keeps happening
7. Reload the tab and the same behaviour happens
8. Shift+Reload the tab and I am presented with the Unsupported Browser page and the Browser Console shows these errors about localstorage:
```
/sync error ConnectionError: fetch failed: NetworkError when attempting to fetch resource. vendors~init.js:2:2569493
r https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
methodFactory https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
onSyncError https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
doSync https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
sync https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
startClient https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
start https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
ue https://staging.element.io/bundles/51733431847a348f8b7e/vendors~element-web-app.js:2
ie https://staging.element.io/bundles/51733431847a348f8b7e/vendors~element-web-app.js:2
ee https://staging.element.io/bundles/51733431847a348f8b7e/vendors~element-web-app.js:2
K https://staging.element.io/bundles/51733431847a348f8b7e/vendors~element-web-app.js:2
loadSession https://staging.element.io/bundles/51733431847a348f8b7e/vendors~element-web-app.js:2
(Async: promise callback)
loadSession https://staging.element.io/bundles/51733431847a348f8b7e/vendors~element-web-app.js:2
Ke https://staging.element.io/bundles/51733431847a348f8b7e/vendors~element-web-app.js:2
(Async: promise callback)
Ke https://staging.element.io/bundles/51733431847a348f8b7e/vendors~element-web-app.js:2
yo https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
Va https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
Ws https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
Ol https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
Dl https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
Fl https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
vl https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
ml https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
ec https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
ac https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
El https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
ac https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
render https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
ne https://staging.element.io/bundles/51733431847a348f8b7e/init.js:1
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
s https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
Browser missing feature: 'localstorage' bundle.js:2:6903
methodFactory https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
s https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
s https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
Failed to open log database: InvalidStateError vendors~init.js:2:2569493
r https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
methodFactory https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
onerror https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
(Async: EventHandlerNonNull)
connect https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
connect https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
h https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
X https://staging.element.io/bundles/51733431847a348f8b7e/init.js:1
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
s https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
Uncaught (in promise) Error: Failed to open log database: InvalidStateError
onerror https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
connect https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
connect https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
h https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
X https://staging.element.io/bundles/51733431847a348f8b7e/init.js:1
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
async* https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
s https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
Browser is missing required features. vendors~init.js:2:2569493
r https://staging.element.io/bundles/51733431847a348f8b7e/vendors~init.js:2
methodFactory https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
s https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
<anonymous> https://staging.element.io/bundles/51733431847a348f8b7e/bundle.js:2
```
Closing the Private Browsing window and trying again eventually fixes it, although I can keep reloading the page and eventually get the Unsupported Browser page. It works intermittently, maybe about half the time in my initial testing.
### Outcome
#### What did you expect?
Room content should load in Private Browsing mode
#### What happened instead?
Room content fails to load, all I see is the Welcome screen:

If I reload the page I eventually get an Unsupported Browser prompt.

### Operating system
OpenSUSE Tumbleweed 20230111 (Linux)
### Browser information
Firefox 108.0.2
### URL for webapp
staging.element.io
### Application version
Element version: 1.11.18-rc.3, Olm version: 3.2.12
### Homeserver
element.io
### Will you send logs?
No | defect | staging fails to load room content with firefox private browsing steps to reproduce open staging element io in firefox private browsing log in using sso and verify the session click a room that is already open in the sidebar the welcome to element screen stays open and the room is not displayed and i get these errors in the browser console error handling m room key event quotaexceedederror the quota has been exceeded vendors init js r methodfactory onroomkeyevent error uploading one time keys v storeaccount storeaccount storeaccount generateonetimekeys getaccount getaccount getaccount getaccount generateonetimekeys dotxn dotxn generateonetimekeys r maybeuploadonetimekeys uncaught in promise domexception the quota has been exceeded vendors element web app js keep trying to switch between rooms and the same thing keeps happening reload the tab and the same behaviour happens shift reload the tab and i am presented with the unsupported browser page and the browser console shows these errors about localstorage sync error connectionerror fetch failed networkerror when attempting to fetch resource vendors init js r methodfactory onsyncerror dosync sync startclient start ue ie ee k loadsession async promise callback loadsession ke async promise callback ke yo va ws ol dl fl vl ml ec ac el ac render ne s browser missing feature localstorage bundle js methodfactory s s failed to open log database invalidstateerror vendors init js r methodfactory onerror async eventhandlernonnull connect connect h x s uncaught in promise error failed to open log database invalidstateerror onerror connect connect h x async s browser is missing required features vendors init js r methodfactory s closing the private browsing window and trying again eventually fixes it although i can keep reloading the page and eventually get the unsupported browser page it works intermittently maybe about half the time in my initial testing outcome what did you expect room content should load in private browsing mode what happened instead room content fails to load all i see is the welcome screen if i reload the page i eventually get an unsupported browser prompt operating system opensuse tumbleweed linux browser information firefox url for webapp staging element io application version element version rc olm version homeserver element io will you send logs no | 1 |
11,457 | 2,651,795,787 | IssuesEvent | 2015-03-16 14:02:32 | cfpb/hmda-pilot | https://api.github.com/repos/cfpb/hmda-pilot | closed | Can we change the instruction wrapping in the detailed edit report? | defect est:2 ui | The instruction sentence wraps pretty far to the left of the screen in the detailed edit reports. Can we change this so that the wrapping follows the same wrapping as the edit description?
Sentence with wrapping issue:
> Please review and correct all errors listed below (1 entry) in your system of record. Once corrected, re-select the updated file to validate the data.
This looks okay when the edit description is short:

But not great when the edit description is longer:

| 1.0 | Can we change the instruction wrapping in the detailed edit report? - The instruction sentence wraps pretty far to the left of the screen in the detailed edit reports. Can we change this so that the wrapping follows the same wrapping as the edit description?
Sentence with wrapping issue:
> Please review and correct all errors listed below (1 entry) in your system of record. Once corrected, re-select the updated file to validate the data.
This looks okay when the edit description is short:

But not great when the edit description is longer:

| defect | can we change the instruction wrapping in the detailed edit report the instruction sentence wraps pretty far to the left of the screen in the detailed edit reports can we change this so that the wrapping follows the same wrapping as the edit description sentence with wrapping issue please review and correct all errors listed below entry in your system of record once corrected re select the updated file to validate the data this looks okay when the edit description is short but not great when the edit description is longer | 1 |
72,481 | 15,237,764,528 | IssuesEvent | 2021-02-19 00:21:30 | 1Blackdiamondsc/BlackDiamond-SC | https://api.github.com/repos/1Blackdiamondsc/BlackDiamond-SC | opened | CVE-2020-11023 (Medium) detected in jquery-3.1.1.slim.min.js | security vulnerability | ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-3.1.1.slim.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.1/jquery.slim.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.1/jquery.slim.min.js</a></p>
<p>Path to dependency file: BlackDiamond-SC/node_modules/eol/index.html</p>
<p>Path to vulnerable library: BlackDiamond-SC/node_modules/eol/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.1.1.slim.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/1Blackdiamondsc/BlackDiamond-SC/commit/c207c86fd986bb1fa43f5a48ab214128c252cac8">c207c86fd986bb1fa43f5a48ab214128c252cac8</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-11023 (Medium) detected in jquery-3.1.1.slim.min.js - ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-3.1.1.slim.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.1/jquery.slim.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.1/jquery.slim.min.js</a></p>
<p>Path to dependency file: BlackDiamond-SC/node_modules/eol/index.html</p>
<p>Path to vulnerable library: BlackDiamond-SC/node_modules/eol/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.1.1.slim.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/1Blackdiamondsc/BlackDiamond-SC/commit/c207c86fd986bb1fa43f5a48ab214128c252cac8">c207c86fd986bb1fa43f5a48ab214128c252cac8</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_defect | cve medium detected in jquery slim min js cve medium severity vulnerability vulnerable library jquery slim min js javascript library for dom operations library home page a href path to dependency file blackdiamond sc node modules eol index html path to vulnerable library blackdiamond sc node modules eol index html dependency hierarchy x jquery slim min js vulnerable library found in head commit a href found in base branch main vulnerability details in jquery versions greater than or equal to and before passing html containing elements from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource | 0 |
1,523 | 2,605,257,207 | IssuesEvent | 2015-02-25 05:20:26 | jekyll/jekyll | https://api.github.com/repos/jekyll/jekyll | closed | Add "Edit this Page" links to documentation | Documentation | @benbalter has a couple cool pieces on his website:

and

People reading his blog can go and suggest edits to his blog posts with one click. I'd love to have a feature like this on jekyllrb.com | 1.0 | Add "Edit this Page" links to documentation - @benbalter has a couple cool pieces on his website:

and

People reading his blog can go and suggest edits to his blog posts with one click. I'd love to have a feature like this on jekyllrb.com | non_defect | add edit this page links to documentation benbalter has a couple cool pieces on his website and people reading his blog can go and suggest edits to his blog posts with one click i d love to have a feature like this on jekyllrb com | 0 |
304,588 | 23,073,217,606 | IssuesEvent | 2022-07-25 20:14:59 | open-feature/docs.openfeature.dev | https://api.github.com/repos/open-feature/docs.openfeature.dev | closed | Intro doc page | documentation | - Should explain feature-flagging itself at a high level (link to Pete's blog?)
- Should explain goals at high level
- Should enumerate all relevant abstractions at a high level, and eventually provide links (evaluation API, context, providers, hooks)
| 1.0 | Intro doc page - - Should explain feature-flagging itself at a high level (link to Pete's blog?)
- Should explain goals at high level
- Should enumerate all relevant abstractions at a high level, and eventually provide links (evaluation API, context, providers, hooks)
| non_defect | intro doc page should explain feature flagging itself at a high level link to pete s blog should explain goals at high level should enumerate all relevant abstractions at a high level and eventually provide links evaluation api context providers hooks | 0 |
747,669 | 26,094,971,189 | IssuesEvent | 2022-12-26 17:49:47 | bounswe/bounswe2022group9 | https://api.github.com/repos/bounswe/bounswe2022group9 | closed | [Frontend] - Search Art Item Implementation | Enhancement Priority: High Completed Frontend | Search on art items tags and descriptions.
Deadline: 19.12.2022 | 1.0 | [Frontend] - Search Art Item Implementation - Search on art items tags and descriptions.
Deadline: 19.12.2022 | non_defect | search art item implementation search on art items tags and descriptions deadline | 0 |
70,218 | 23,054,601,818 | IssuesEvent | 2022-07-25 02:30:56 | cakephp/cakephp | https://api.github.com/repos/cakephp/cakephp | closed | Pass "-1" in the url as an int-type parameter | controller defect | ### Description
### Steps to reproduce
1. Create a function that accept int as a parameter.
```php
public function view(int $id) {
...
}
```
2. Pass `-1` in the url e.g., `http://localhost/blogs/view/-1`
3. This is an error on screen
```
Unable to coerce "-1" to `int` for `id` in action BlogsController::view().
```
### Proposed fix
Changing this line `return ctype_digit($argument) ? (int)$argument : null;` from [ControllerFactory.php#L271](https://github.com/cakephp/cakephp/blob/4.x/src/Controller/ControllerFactory.php#L271)
To:
```php
return filter_var($argument, FILTER_VALIDATE_INT) !== false ? (int)$argument : null;
```
Tested: https://onlinephp.io/c/16865
### CakePHP Version
4.4.1
### PHP Version
7.4 | 1.0 | Pass "-1" in the url as an int-type parameter - ### Description
### Steps to reproduce
1. Create a function that accept int as a parameter.
```php
public function view(int $id) {
...
}
```
2. Pass `-1` in the url e.g., `http://localhost/blogs/view/-1`
3. This is an error on screen
```
Unable to coerce "-1" to `int` for `id` in action BlogsController::view().
```
### Proposed fix
Changing this line `return ctype_digit($argument) ? (int)$argument : null;` from [ControllerFactory.php#L271](https://github.com/cakephp/cakephp/blob/4.x/src/Controller/ControllerFactory.php#L271)
To:
```php
return filter_var($argument, FILTER_VALIDATE_INT) !== false ? (int)$argument : null;
```
Tested: https://onlinephp.io/c/16865
### CakePHP Version
4.4.1
### PHP Version
7.4 | defect | pass in the url as an int type parameter description steps to reproduce create a function that accept int as a parameter php public function view int id pass in the url e g this is an error on screen unable to coerce to int for id in action blogscontroller view proposed fix changing this line return ctype digit argument int argument null from to php return filter var argument filter validate int false int argument null tested cakephp version php version | 1 |
827,569 | 31,779,088,856 | IssuesEvent | 2023-09-12 16:08:00 | etjump/etjump | https://api.github.com/repos/etjump/etjump | closed | New timerun PBs are no longer sent to all clients | Bug Priority: Normal | When a player gets a new PB, a popup message should be sent to all clients. Now only player itself and spectating clients get the popup. | 1.0 | New timerun PBs are no longer sent to all clients - When a player gets a new PB, a popup message should be sent to all clients. Now only player itself and spectating clients get the popup. | non_defect | new timerun pbs are no longer sent to all clients when a player gets a new pb a popup message should be sent to all clients now only player itself and spectating clients get the popup | 0 |
250,643 | 27,108,654,927 | IssuesEvent | 2023-02-15 13:56:22 | dmyers87/amundsenfrontendlibrary | https://api.github.com/repos/dmyers87/amundsenfrontendlibrary | opened | CVE-2023-25577 (High) detected in Werkzeug-1.0.1-py2.py3-none-any.whl | security vulnerability | ## CVE-2023-25577 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Werkzeug-1.0.1-py2.py3-none-any.whl</b></p></summary>
<p>The comprehensive WSGI web application library.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/cc/94/5f7079a0e00bd6863ef8f1da638721e9da21e5bacee597595b318f71d62e/Werkzeug-1.0.1-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/cc/94/5f7079a0e00bd6863ef8f1da638721e9da21e5bacee597595b318f71d62e/Werkzeug-1.0.1-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- Flask_RESTful-0.3.7-py2.py3-none-any.whl (Root Library)
- Flask-1.0.2-py2.py3-none-any.whl
- :x: **Werkzeug-1.0.1-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Werkzeug is a comprehensive WSGI web application library. Prior to version 2.2.3, Werkzeug's multipart form data parser will parse an unlimited number of parts, including file parts. Parts can be a small amount of bytes, but each requires CPU time to parse and may use more memory as Python data. If a request can be made to an endpoint that accesses `request.data`, `request.form`, `request.files`, or `request.get_data(parse_form_data=False)`, it can cause unexpectedly high resource usage. This allows an attacker to cause a denial of service by sending crafted multipart data to an endpoint that will parse it. The amount of CPU time required can block worker processes from handling legitimate requests. The amount of RAM required can trigger an out of memory kill of the process. Unlimited file parts can use up memory and file handles. If many concurrent requests are sent continuously, this can exhaust or kill all available workers. Version 2.2.3 contains a patch for this issue.
<p>Publish Date: 2023-02-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-25577>CVE-2023-25577</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2023-25577">https://www.cve.org/CVERecord?id=CVE-2023-25577</a></p>
<p>Release Date: 2023-02-14</p>
<p>Fix Resolution: Werkzeug - 2.2.3</p>
</p>
</details>
<p></p>
| True | CVE-2023-25577 (High) detected in Werkzeug-1.0.1-py2.py3-none-any.whl - ## CVE-2023-25577 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Werkzeug-1.0.1-py2.py3-none-any.whl</b></p></summary>
<p>The comprehensive WSGI web application library.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/cc/94/5f7079a0e00bd6863ef8f1da638721e9da21e5bacee597595b318f71d62e/Werkzeug-1.0.1-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/cc/94/5f7079a0e00bd6863ef8f1da638721e9da21e5bacee597595b318f71d62e/Werkzeug-1.0.1-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- Flask_RESTful-0.3.7-py2.py3-none-any.whl (Root Library)
- Flask-1.0.2-py2.py3-none-any.whl
- :x: **Werkzeug-1.0.1-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Werkzeug is a comprehensive WSGI web application library. Prior to version 2.2.3, Werkzeug's multipart form data parser will parse an unlimited number of parts, including file parts. Parts can be a small amount of bytes, but each requires CPU time to parse and may use more memory as Python data. If a request can be made to an endpoint that accesses `request.data`, `request.form`, `request.files`, or `request.get_data(parse_form_data=False)`, it can cause unexpectedly high resource usage. This allows an attacker to cause a denial of service by sending crafted multipart data to an endpoint that will parse it. The amount of CPU time required can block worker processes from handling legitimate requests. The amount of RAM required can trigger an out of memory kill of the process. Unlimited file parts can use up memory and file handles. If many concurrent requests are sent continuously, this can exhaust or kill all available workers. Version 2.2.3 contains a patch for this issue.
<p>Publish Date: 2023-02-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-25577>CVE-2023-25577</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2023-25577">https://www.cve.org/CVERecord?id=CVE-2023-25577</a></p>
<p>Release Date: 2023-02-14</p>
<p>Fix Resolution: Werkzeug - 2.2.3</p>
</p>
</details>
<p></p>
| non_defect | cve high detected in werkzeug none any whl cve high severity vulnerability vulnerable library werkzeug none any whl the comprehensive wsgi web application library library home page a href path to dependency file requirements txt path to vulnerable library requirements txt dependency hierarchy flask restful none any whl root library flask none any whl x werkzeug none any whl vulnerable library found in base branch master vulnerability details werkzeug is a comprehensive wsgi web application library prior to version werkzeug s multipart form data parser will parse an unlimited number of parts including file parts parts can be a small amount of bytes but each requires cpu time to parse and may use more memory as python data if a request can be made to an endpoint that accesses request data request form request files or request get data parse form data false it can cause unexpectedly high resource usage this allows an attacker to cause a denial of service by sending crafted multipart data to an endpoint that will parse it the amount of cpu time required can block worker processes from handling legitimate requests the amount of ram required can trigger an out of memory kill of the process unlimited file parts can use up memory and file handles if many concurrent requests are sent continuously this can exhaust or kill all available workers version contains a patch for this issue publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution werkzeug | 0 |
31,492 | 6,539,714,002 | IssuesEvent | 2017-09-01 12:38:49 | CenturyLinkCloud/mdw | https://api.github.com/repos/CenturyLinkCloud/mdw | closed | Fix Chart Type selection | defect | ng-switch attribute has been removed from from chart.html because chart display was broken when user comes straight to Dashboard instead of navigating from the process list. We can add back the chart type selection as long as it works regardless of navigation. | 1.0 | Fix Chart Type selection - ng-switch attribute has been removed from from chart.html because chart display was broken when user comes straight to Dashboard instead of navigating from the process list. We can add back the chart type selection as long as it works regardless of navigation. | defect | fix chart type selection ng switch attribute has been removed from from chart html because chart display was broken when user comes straight to dashboard instead of navigating from the process list we can add back the chart type selection as long as it works regardless of navigation | 1 |
17,221 | 2,984,441,459 | IssuesEvent | 2015-07-18 01:00:36 | google/omaha | https://api.github.com/repos/google/omaha | closed | IsVistaOrLater() tests only the major version | auto-migrated Priority-Medium Type-Defect | ```
Calling ::VerifyVersionInfo() to test for major version must also include
minor, SP major and SP minor
See MSDN
http://msdn.microsoft.com/en-us/library/windows/desktop/ms725492%28v=vs.85%29.as
px
This is implemented in
omaha\base\vistautil.cc
```
Original issue reported on code.google.com by `nir....@panel-sw.co.il` on 6 Jan 2014 at 5:22 | 1.0 | IsVistaOrLater() tests only the major version - ```
Calling ::VerifyVersionInfo() to test for major version must also include
minor, SP major and SP minor
See MSDN
http://msdn.microsoft.com/en-us/library/windows/desktop/ms725492%28v=vs.85%29.as
px
This is implemented in
omaha\base\vistautil.cc
```
Original issue reported on code.google.com by `nir....@panel-sw.co.il` on 6 Jan 2014 at 5:22 | defect | isvistaorlater tests only the major version calling verifyversioninfo to test for major version must also include minor sp major and sp minor see msdn px this is implemented in omaha base vistautil cc original issue reported on code google com by nir panel sw co il on jan at | 1 |
52,318 | 13,224,649,336 | IssuesEvent | 2020-08-17 19:33:45 | icecube-trac/tix4 | https://api.github.com/repos/icecube-trac/tix4 | opened | [dataio] add docs and unit tests for zstd (Trac #2011) | Incomplete Migration Migrated from Trac combo core defect | <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/2011">https://code.icecube.wisc.edu/projects/icecube/ticket/2011</a>, reported by kjmeagherand owned by jbraun</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:15:23",
"_ts": "1550067323910946",
"description": "tests should include reading and writing. Docs should explain the different compression levels and include plots justifying this algorithm ",
"reporter": "kjmeagher",
"cc": "",
"resolution": "fixed",
"time": "2017-05-09T18:48:18",
"component": "combo core",
"summary": "[dataio] add docs and unit tests for zstd",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "jbraun",
"type": "defect"
}
```
</p>
</details>
| 1.0 | [dataio] add docs and unit tests for zstd (Trac #2011) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/2011">https://code.icecube.wisc.edu/projects/icecube/ticket/2011</a>, reported by kjmeagherand owned by jbraun</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:15:23",
"_ts": "1550067323910946",
"description": "tests should include reading and writing. Docs should explain the different compression levels and include plots justifying this algorithm ",
"reporter": "kjmeagher",
"cc": "",
"resolution": "fixed",
"time": "2017-05-09T18:48:18",
"component": "combo core",
"summary": "[dataio] add docs and unit tests for zstd",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "jbraun",
"type": "defect"
}
```
</p>
</details>
| defect | add docs and unit tests for zstd trac migrated from json status closed changetime ts description tests should include reading and writing docs should explain the different compression levels and include plots justifying this algorithm reporter kjmeagher cc resolution fixed time component combo core summary add docs and unit tests for zstd priority normal keywords milestone owner jbraun type defect | 1 |
42,089 | 10,799,130,348 | IssuesEvent | 2019-11-06 11:28:26 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | opened | Exception encountered by TimedMemberStateFactory stops MC service | Team: Management Center Type: Defect | `ManagementCenterService` shuts down itself if it encounters an exception when creating the `TimedMemberState`. This issue makes the cluster to disappear from MC. The related code is here: https://github.com/hazelcast/hazelcast/blob/91ae6c327b9c2e8f73e95a1ffadfeba090267272/hazelcast/src/main/java/com/hazelcast/internal/management/ManagementCenterService.java#L447-L460
This happens even if the exception is a retryable one such as in this case:
```
[127.0.0.1]:5702 [A] [4.0-SNAPSHOT] Hazelcast Management Center Service will be shutdown due to exception.
com.hazelcast.spi.exception.RetryableHazelcastException: HazelcastInstance[[127.0.0.1]:5702] is not active!
at com.hazelcast.spi.impl.NodeEngineImpl.getService(NodeEngineImpl.java:385) ~[hazelcast-4.0-SNAPSHOT.jar:4.0-SNAPSHOT]
at com.hazelcast.internal.management.TimedMemberStateFactory.getCacheService(TimedMemberStateFactory.java:422) ~[hazelcast-4.0-SNAPSHOT.jar:4.0-SNAPSHOT]
at com.hazelcast.internal.management.TimedMemberStateFactory.createMemState(TimedMemberStateFactory.java:278) ~[hazelcast-4.0-SNAPSHOT.jar:4.0-SNAPSHOT]
at com.hazelcast.internal.management.TimedMemberStateFactory.createMemberState(TimedMemberStateFactory.java:200) ~[hazelcast-4.0-SNAPSHOT.jar:4.0-SNAPSHOT]
at com.hazelcast.internal.management.TimedMemberStateFactory.createTimedMemberState(TimedMemberStateFactory.java:126) ~[hazelcast-4.0-SNAPSHOT.jar:4.0-SNAPSHOT]
at com.hazelcast.internal.management.ManagementCenterService$PrepareStateThread.run(ManagementCenterService.java:450) [hazelcast-4.0-SNAPSHOT.jar:4.0-SNAPSHOT]
```
Related closed issue #15656 | 1.0 | Exception encountered by TimedMemberStateFactory stops MC service - `ManagementCenterService` shuts down itself if it encounters an exception when creating the `TimedMemberState`. This issue makes the cluster to disappear from MC. The related code is here: https://github.com/hazelcast/hazelcast/blob/91ae6c327b9c2e8f73e95a1ffadfeba090267272/hazelcast/src/main/java/com/hazelcast/internal/management/ManagementCenterService.java#L447-L460
This happens even if the exception is a retryable one such as in this case:
```
[127.0.0.1]:5702 [A] [4.0-SNAPSHOT] Hazelcast Management Center Service will be shutdown due to exception.
com.hazelcast.spi.exception.RetryableHazelcastException: HazelcastInstance[[127.0.0.1]:5702] is not active!
at com.hazelcast.spi.impl.NodeEngineImpl.getService(NodeEngineImpl.java:385) ~[hazelcast-4.0-SNAPSHOT.jar:4.0-SNAPSHOT]
at com.hazelcast.internal.management.TimedMemberStateFactory.getCacheService(TimedMemberStateFactory.java:422) ~[hazelcast-4.0-SNAPSHOT.jar:4.0-SNAPSHOT]
at com.hazelcast.internal.management.TimedMemberStateFactory.createMemState(TimedMemberStateFactory.java:278) ~[hazelcast-4.0-SNAPSHOT.jar:4.0-SNAPSHOT]
at com.hazelcast.internal.management.TimedMemberStateFactory.createMemberState(TimedMemberStateFactory.java:200) ~[hazelcast-4.0-SNAPSHOT.jar:4.0-SNAPSHOT]
at com.hazelcast.internal.management.TimedMemberStateFactory.createTimedMemberState(TimedMemberStateFactory.java:126) ~[hazelcast-4.0-SNAPSHOT.jar:4.0-SNAPSHOT]
at com.hazelcast.internal.management.ManagementCenterService$PrepareStateThread.run(ManagementCenterService.java:450) [hazelcast-4.0-SNAPSHOT.jar:4.0-SNAPSHOT]
```
Related closed issue #15656 | defect | exception encountered by timedmemberstatefactory stops mc service managementcenterservice shuts down itself if it encounters an exception when creating the timedmemberstate this issue makes the cluster to disappear from mc the related code is here this happens even if the exception is a retryable one such as in this case hazelcast management center service will be shutdown due to exception com hazelcast spi exception retryablehazelcastexception hazelcastinstance is not active at com hazelcast spi impl nodeengineimpl getservice nodeengineimpl java at com hazelcast internal management timedmemberstatefactory getcacheservice timedmemberstatefactory java at com hazelcast internal management timedmemberstatefactory creatememstate timedmemberstatefactory java at com hazelcast internal management timedmemberstatefactory creatememberstate timedmemberstatefactory java at com hazelcast internal management timedmemberstatefactory createtimedmemberstate timedmemberstatefactory java at com hazelcast internal management managementcenterservice preparestatethread run managementcenterservice java related closed issue | 1 |
48,078 | 13,067,430,327 | IssuesEvent | 2020-07-31 00:25:47 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | closed | [steamshovel] can't leave icetop viewer (Trac #1744) | Migrated from Trac cmake defect | On my Mac running El Cap with the current trunk, whenever I click on the IceTopViewer checkbox it switches to IceTopViewer mode but gets stuck there. The checkbox appears unresponsive. Closing steamshovel and deleting the config files seems to be the only way to restore working order. The issue might be related to the fact that the PulseSeries in question has no IceTop pulses.
Migrated from https://code.icecube.wisc.edu/ticket/1744
```json
{
"status": "closed",
"changetime": "2016-06-14T14:48:50",
"description": "On my Mac running El Cap with the current trunk, whenever I click on the IceTopViewer checkbox it switches to IceTopViewer mode but gets stuck there. The checkbox appears unresponsive. Closing steamshovel and deleting the config files seems to be the only way to restore working order. The issue might be related to the fact that the PulseSeries in question has no IceTop pulses.",
"reporter": "kjmeagher",
"cc": "",
"resolution": "invalid",
"_ts": "1465915730114312",
"component": "cmake",
"summary": "[steamshovel] can't leave icetop viewer",
"priority": "normal",
"keywords": "steamshovel",
"time": "2016-06-14T07:55:42",
"milestone": "",
"owner": "hdembinski",
"type": "defect"
}
```
| 1.0 | [steamshovel] can't leave icetop viewer (Trac #1744) - On my Mac running El Cap with the current trunk, whenever I click on the IceTopViewer checkbox it switches to IceTopViewer mode but gets stuck there. The checkbox appears unresponsive. Closing steamshovel and deleting the config files seems to be the only way to restore working order. The issue might be related to the fact that the PulseSeries in question has no IceTop pulses.
Migrated from https://code.icecube.wisc.edu/ticket/1744
```json
{
"status": "closed",
"changetime": "2016-06-14T14:48:50",
"description": "On my Mac running El Cap with the current trunk, whenever I click on the IceTopViewer checkbox it switches to IceTopViewer mode but gets stuck there. The checkbox appears unresponsive. Closing steamshovel and deleting the config files seems to be the only way to restore working order. The issue might be related to the fact that the PulseSeries in question has no IceTop pulses.",
"reporter": "kjmeagher",
"cc": "",
"resolution": "invalid",
"_ts": "1465915730114312",
"component": "cmake",
"summary": "[steamshovel] can't leave icetop viewer",
"priority": "normal",
"keywords": "steamshovel",
"time": "2016-06-14T07:55:42",
"milestone": "",
"owner": "hdembinski",
"type": "defect"
}
```
| defect | can t leave icetop viewer trac on my mac running el cap with the current trunk whenever i click on the icetopviewer checkbox it switches to icetopviewer mode but gets stuck there the checkbox appears unresponsive closing steamshovel and deleting the config files seems to be the only way to restore working order the issue might be related to the fact that the pulseseries in question has no icetop pulses migrated from json status closed changetime description on my mac running el cap with the current trunk whenever i click on the icetopviewer checkbox it switches to icetopviewer mode but gets stuck there the checkbox appears unresponsive closing steamshovel and deleting the config files seems to be the only way to restore working order the issue might be related to the fact that the pulseseries in question has no icetop pulses reporter kjmeagher cc resolution invalid ts component cmake summary can t leave icetop viewer priority normal keywords steamshovel time milestone owner hdembinski type defect | 1 |
533,656 | 15,596,289,436 | IssuesEvent | 2021-03-18 15:43:02 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | tinder.com - see bug description | browser-firefox engine-gecko ml-needsdiagnosis-false ml-probability-high priority-normal | <!-- @browser: Firefox 87.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:87.0) Gecko/20100101 Firefox/87.0 -->
<!-- @reported_with: desktop-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/68440 -->
**URL**: https://tinder.com/app/recs
**Browser / Version**: Firefox 87.0
**Operating System**: Windows 10
**Tested Another Browser**: Yes Chrome
**Problem type**: Something else
**Description**: location
**Steps to Reproduce**:
Can't access to Tinder cos Location is not Allowed
<details>
<summary>View the screenshot</summary>
<img alt="Screenshot" src="https://webcompat.com/uploads/2021/3/789e941a-e569-4f56-92cb-b92537eb19c3.jpeg">
</details>
<details>
<summary>Browser Configuration</summary>
<ul>
<li>gfx.webrender.all: false</li><li>gfx.webrender.blob-images: true</li><li>gfx.webrender.enabled: false</li><li>image.mem.shared: true</li><li>buildID: 20210307185839</li><li>channel: beta</li><li>hasTouchScreen: false</li><li>mixed active content blocked: false</li><li>mixed passive content blocked: false</li><li>tracking content blocked: false</li>
</ul>
</details>
[View console log messages](https://webcompat.com/console_logs/2021/3/031be63b-6379-4386-a297-b7b1f725fa45)
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | tinder.com - see bug description - <!-- @browser: Firefox 87.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:87.0) Gecko/20100101 Firefox/87.0 -->
<!-- @reported_with: desktop-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/68440 -->
**URL**: https://tinder.com/app/recs
**Browser / Version**: Firefox 87.0
**Operating System**: Windows 10
**Tested Another Browser**: Yes Chrome
**Problem type**: Something else
**Description**: location
**Steps to Reproduce**:
Can't access to Tinder cos Location is not Allowed
<details>
<summary>View the screenshot</summary>
<img alt="Screenshot" src="https://webcompat.com/uploads/2021/3/789e941a-e569-4f56-92cb-b92537eb19c3.jpeg">
</details>
<details>
<summary>Browser Configuration</summary>
<ul>
<li>gfx.webrender.all: false</li><li>gfx.webrender.blob-images: true</li><li>gfx.webrender.enabled: false</li><li>image.mem.shared: true</li><li>buildID: 20210307185839</li><li>channel: beta</li><li>hasTouchScreen: false</li><li>mixed active content blocked: false</li><li>mixed passive content blocked: false</li><li>tracking content blocked: false</li>
</ul>
</details>
[View console log messages](https://webcompat.com/console_logs/2021/3/031be63b-6379-4386-a297-b7b1f725fa45)
_From [webcompat.com](https://webcompat.com/) with ❤️_ | non_defect | tinder com see bug description url browser version firefox operating system windows tested another browser yes chrome problem type something else description location steps to reproduce can t access to tinder cos location is not allowed view the screenshot img alt screenshot src browser configuration gfx webrender all false gfx webrender blob images true gfx webrender enabled false image mem shared true buildid channel beta hastouchscreen false mixed active content blocked false mixed passive content blocked false tracking content blocked false from with ❤️ | 0 |
40,009 | 9,793,770,026 | IssuesEvent | 2019-06-10 20:48:29 | gitblit/gitblit | https://api.github.com/repos/gitblit/gitblit | closed | special chars in folders name | Priority-Medium Status-Accepted Type-Defect | I have a folder named "[logs]". When I try to open it with gitblit, it returns:
"Internal error"
How can I solve it?
thank you
| 1.0 | special chars in folders name - I have a folder named "[logs]". When I try to open it with gitblit, it returns:
"Internal error"
How can I solve it?
thank you
| defect | special chars in folders name i have a folder named when i try to open it with gitblit it returns internal error how can i solve it thank you | 1 |
14,524 | 2,814,658,270 | IssuesEvent | 2015-05-18 21:16:51 | NREL/EnergyPlus | https://api.github.com/repos/NREL/EnergyPlus | closed | Coefficients in the cross ventilation model should be updated. (CR #9381) | Defect EnergyPlus fixed Priority S2 - Medium | #### Update coefficients in the cross ventilation model
###### Added on 2013-11-13 01:24 by @hongtz68
--
#### Description
Guilherme and Nick made some modifications to the coefficients in the cross ventilation model updated in EnergyPlus 8.1.
TH 11/25/2013
only changes are the following in RoomAirModelCrossVent.f90:
REAL(r64),PARAMETER :: Cjet1 = 1.873d0 ! First correlation constant for the jet velocity
REAL(r64),PARAMETER :: Cjet2 = 0.243d0 ! Second correlation constant for the jet velocity
REAL(r64),PARAMETER :: Crec1 = 0.591d0 ! First correlation constant for the recirculation velocity
REAL(r64),PARAMETER :: Crec2 = 0.070d0 ! Second correlation constant for the recirculation velocity
REAL(r64),PARAMETER :: CjetTemp = 0.849d0 ! Correlation constant for the jet temperature rise
REAL(r64),PARAMETER :: CrecTemp = 1.385d0 ! Correlation constant for the recirculation temperature rise
REAL(r64),PARAMETER :: CrecFlow1 = 0.415d0 ! First correlation constant for the recirculation flow rate
REAL(r64),PARAMETER :: CrecFlow2 = 0.466d0 ! Second correlation constant for the recirculation flow rate
--
Addressed in `Next Build` by @hongtz68
Last build tested: `13.10.18 V8.1.0.008` | 1.0 | Coefficients in the cross ventilation model should be updated. (CR #9381) - #### Update coefficients in the cross ventilation model
###### Added on 2013-11-13 01:24 by @hongtz68
--
#### Description
Guilherme and Nick made some modifications to the coefficients in the cross ventilation model updated in EnergyPlus 8.1.
TH 11/25/2013
only changes are the following in RoomAirModelCrossVent.f90:
REAL(r64),PARAMETER :: Cjet1 = 1.873d0 ! First correlation constant for the jet velocity
REAL(r64),PARAMETER :: Cjet2 = 0.243d0 ! Second correlation constant for the jet velocity
REAL(r64),PARAMETER :: Crec1 = 0.591d0 ! First correlation constant for the recirculation velocity
REAL(r64),PARAMETER :: Crec2 = 0.070d0 ! Second correlation constant for the recirculation velocity
REAL(r64),PARAMETER :: CjetTemp = 0.849d0 ! Correlation constant for the jet temperature rise
REAL(r64),PARAMETER :: CrecTemp = 1.385d0 ! Correlation constant for the recirculation temperature rise
REAL(r64),PARAMETER :: CrecFlow1 = 0.415d0 ! First correlation constant for the recirculation flow rate
REAL(r64),PARAMETER :: CrecFlow2 = 0.466d0 ! Second correlation constant for the recirculation flow rate
--
Addressed in `Next Build` by @hongtz68
Last build tested: `13.10.18 V8.1.0.008` | defect | coefficients in the cross ventilation model should be updated cr update coefficients in the cross ventilation model added on by description guilherme and nick made some modifications to the coefficients in the cross ventilation model updated in energyplus th only changes are the following in roomairmodelcrossvent real parameter first correlation constant for the jet velocity real parameter second correlation constant for the jet velocity real parameter first correlation constant for the recirculation velocity real parameter second correlation constant for the recirculation velocity real parameter cjettemp correlation constant for the jet temperature rise real parameter crectemp correlation constant for the recirculation temperature rise real parameter first correlation constant for the recirculation flow rate real parameter second correlation constant for the recirculation flow rate addressed in next build by last build tested | 1 |
50,163 | 13,505,877,361 | IssuesEvent | 2020-09-14 01:04:42 | LevyForchh/gvisor | https://api.github.com/repos/LevyForchh/gvisor | opened | CVE-2020-15168 (Low) detected in node-fetch-2.6.0.tgz, node-fetch-1.7.3.tgz | security vulnerability | ## CVE-2020-15168 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-fetch-2.6.0.tgz</b>, <b>node-fetch-1.7.3.tgz</b></p></summary>
<p>
<details><summary><b>node-fetch-2.6.0.tgz</b></p></summary>
<p>A light-weight module that brings window.fetch to node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.0.tgz">https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.0.tgz</a></p>
<p>Path to dependency file: gvisor/benchmarks/workloads/node/package.json</p>
<p>Path to vulnerable library: gvisor/benchmarks/workloads/node/node_modules/node-fetch/package.json</p>
<p>
Dependency Hierarchy:
- logging-4.5.2.tgz (Root Library)
- gcp-metadata-1.0.0.tgz
- gaxios-1.8.4.tgz
- :x: **node-fetch-2.6.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>node-fetch-1.7.3.tgz</b></p></summary>
<p>A light-weight module that brings window.fetch to node.js and io.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-fetch/-/node-fetch-1.7.3.tgz">https://registry.npmjs.org/node-fetch/-/node-fetch-1.7.3.tgz</a></p>
<p>Path to dependency file: gvisor/benchmarks/workloads/node/package.json</p>
<p>Path to vulnerable library: gvisor/benchmarks/workloads/node/node_modules/isomorphic-fetch/node_modules/node-fetch/package.json</p>
<p>
Dependency Hierarchy:
- firebase-5.11.1.tgz (Root Library)
- functions-0.4.6.tgz
- isomorphic-fetch-2.2.1.tgz
- :x: **node-fetch-1.7.3.tgz** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
node-fetch before versions 2.6.1 and 3.0.0-beta.9 did not honor the size option after following a redirect, which means that when a content size was over the limit, a FetchError would never get thrown and the process would end without failure. For most people, this fix will have a little or no impact. However, if you are relying on node-fetch to gate files above a size, the impact could be significant, for example: If you don't double-check the size of the data after fetch() has completed, your JS thread could get tied up doing work on a large file (DoS) and/or cost you money in computing.
<p>Publish Date: 2020-07-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15168>CVE-2020-15168</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>2.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/node-fetch/node-fetch/security/advisories/GHSA-w7rc-rwvf-8q5r">https://github.com/node-fetch/node-fetch/security/advisories/GHSA-w7rc-rwvf-8q5r</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: 2.6.1,3.0.0-beta.9</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-fetch","packageVersion":"2.6.0","isTransitiveDependency":true,"dependencyTree":"@google-cloud/logging:4.5.2;gcp-metadata:1.0.0;gaxios:1.8.4;node-fetch:2.6.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.6.1,3.0.0-beta.9"},{"packageType":"javascript/Node.js","packageName":"node-fetch","packageVersion":"1.7.3","isTransitiveDependency":true,"dependencyTree":"firebase:5.11.1;@firebase/functions:0.4.6;isomorphic-fetch:2.2.1;node-fetch:1.7.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.6.1,3.0.0-beta.9"}],"vulnerabilityIdentifier":"CVE-2020-15168","vulnerabilityDetails":"node-fetch before versions 2.6.1 and 3.0.0-beta.9 did not honor the size option after following a redirect, which means that when a content size was over the limit, a FetchError would never get thrown and the process would end without failure. For most people, this fix will have a little or no impact. However, if you are relying on node-fetch to gate files above a size, the impact could be significant, for example: If you don\u0027t double-check the size of the data after fetch() has completed, your JS thread could get tied up doing work on a large file (DoS) and/or cost you money in computing.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15168","cvss3Severity":"low","cvss3Score":"2.6","cvss3Metrics":{"A":"Low","AC":"High","PR":"Low","S":"Unchanged","C":"None","UI":"Required","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-15168 (Low) detected in node-fetch-2.6.0.tgz, node-fetch-1.7.3.tgz - ## CVE-2020-15168 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-fetch-2.6.0.tgz</b>, <b>node-fetch-1.7.3.tgz</b></p></summary>
<p>
<details><summary><b>node-fetch-2.6.0.tgz</b></p></summary>
<p>A light-weight module that brings window.fetch to node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.0.tgz">https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.0.tgz</a></p>
<p>Path to dependency file: gvisor/benchmarks/workloads/node/package.json</p>
<p>Path to vulnerable library: gvisor/benchmarks/workloads/node/node_modules/node-fetch/package.json</p>
<p>
Dependency Hierarchy:
- logging-4.5.2.tgz (Root Library)
- gcp-metadata-1.0.0.tgz
- gaxios-1.8.4.tgz
- :x: **node-fetch-2.6.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>node-fetch-1.7.3.tgz</b></p></summary>
<p>A light-weight module that brings window.fetch to node.js and io.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-fetch/-/node-fetch-1.7.3.tgz">https://registry.npmjs.org/node-fetch/-/node-fetch-1.7.3.tgz</a></p>
<p>Path to dependency file: gvisor/benchmarks/workloads/node/package.json</p>
<p>Path to vulnerable library: gvisor/benchmarks/workloads/node/node_modules/isomorphic-fetch/node_modules/node-fetch/package.json</p>
<p>
Dependency Hierarchy:
- firebase-5.11.1.tgz (Root Library)
- functions-0.4.6.tgz
- isomorphic-fetch-2.2.1.tgz
- :x: **node-fetch-1.7.3.tgz** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
node-fetch before versions 2.6.1 and 3.0.0-beta.9 did not honor the size option after following a redirect, which means that when a content size was over the limit, a FetchError would never get thrown and the process would end without failure. For most people, this fix will have a little or no impact. However, if you are relying on node-fetch to gate files above a size, the impact could be significant, for example: If you don't double-check the size of the data after fetch() has completed, your JS thread could get tied up doing work on a large file (DoS) and/or cost you money in computing.
<p>Publish Date: 2020-07-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15168>CVE-2020-15168</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>2.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/node-fetch/node-fetch/security/advisories/GHSA-w7rc-rwvf-8q5r">https://github.com/node-fetch/node-fetch/security/advisories/GHSA-w7rc-rwvf-8q5r</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: 2.6.1,3.0.0-beta.9</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-fetch","packageVersion":"2.6.0","isTransitiveDependency":true,"dependencyTree":"@google-cloud/logging:4.5.2;gcp-metadata:1.0.0;gaxios:1.8.4;node-fetch:2.6.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.6.1,3.0.0-beta.9"},{"packageType":"javascript/Node.js","packageName":"node-fetch","packageVersion":"1.7.3","isTransitiveDependency":true,"dependencyTree":"firebase:5.11.1;@firebase/functions:0.4.6;isomorphic-fetch:2.2.1;node-fetch:1.7.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.6.1,3.0.0-beta.9"}],"vulnerabilityIdentifier":"CVE-2020-15168","vulnerabilityDetails":"node-fetch before versions 2.6.1 and 3.0.0-beta.9 did not honor the size option after following a redirect, which means that when a content size was over the limit, a FetchError would never get thrown and the process would end without failure. For most people, this fix will have a little or no impact. However, if you are relying on node-fetch to gate files above a size, the impact could be significant, for example: If you don\u0027t double-check the size of the data after fetch() has completed, your JS thread could get tied up doing work on a large file (DoS) and/or cost you money in computing.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15168","cvss3Severity":"low","cvss3Score":"2.6","cvss3Metrics":{"A":"Low","AC":"High","PR":"Low","S":"Unchanged","C":"None","UI":"Required","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_defect | cve low detected in node fetch tgz node fetch tgz cve low severity vulnerability vulnerable libraries node fetch tgz node fetch tgz node fetch tgz a light weight module that brings window fetch to node js library home page a href path to dependency file gvisor benchmarks workloads node package json path to vulnerable library gvisor benchmarks workloads node node modules node fetch package json dependency hierarchy logging tgz root library gcp metadata tgz gaxios tgz x node fetch tgz vulnerable library node fetch tgz a light weight module that brings window fetch to node js and io js library home page a href path to dependency file gvisor benchmarks workloads node package json path to vulnerable library gvisor benchmarks workloads node node modules isomorphic fetch node modules node fetch package json dependency hierarchy firebase tgz root library functions tgz isomorphic fetch tgz x node fetch tgz vulnerable library vulnerability details node fetch before versions and beta did not honor the size option after following a redirect which means that when a content size was over the limit a fetcherror would never get thrown and the process would end without failure for most people this fix will have a little or no impact however if you are relying on node fetch to gate files above a size the impact could be significant for example if you don t double check the size of the data after fetch has completed your js thread could get tied up doing work on a large file dos and or cost you money in computing publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required low user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution beta isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails node fetch before versions and beta did not honor the size option after following a redirect which means that when a content size was over the limit a fetcherror would never get thrown and the process would end without failure for most people this fix will have a little or no impact however if you are relying on node fetch to gate files above a size the impact could be significant for example if you don double check the size of the data after fetch has completed your js thread could get tied up doing work on a large file dos and or cost you money in computing vulnerabilityurl | 0 |
753,246 | 26,342,097,554 | IssuesEvent | 2023-01-10 18:33:36 | googleapis/nodejs-datastore | https://api.github.com/repos/googleapis/nodejs-datastore | closed | Datastore importing and exporting entities: should export, then import entities failed | priority: p2 type: bug api: datastore flakybot: issue | Note: #996 was also for this test, but it was closed more than 10 days ago. So, I didn't mark it flaky.
----
commit: 465c6cadee9f534b4c29e746674535f00f586390
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/3e2b8e61-ed9d-4602-96d2-243de5c47c46), [Sponge](http://sponge2/3e2b8e61-ed9d-4602-96d2-243de5c47c46)
status: failed
<details><summary>Test output</summary><br><pre>16 UNAUTHENTICATED: Request had invalid authentication credentials. Expected OAuth 2 access token, login cookie or other valid authentication credential. See https://developers.google.com/identity/sign-in/web/devconsole-project.
Error: 16 UNAUTHENTICATED: Request had invalid authentication credentials. Expected OAuth 2 access token, login cookie or other valid authentication credential. See https://developers.google.com/identity/sign-in/web/devconsole-project.
at Object.callErrorFromStatus (node_modules/@grpc/grpc-js/build/src/call.js:31:19)
-> /workspace/node_modules/@grpc/grpc-js/src/call.ts:81:17
at Object.onReceiveStatus (node_modules/@grpc/grpc-js/build/src/client.js:195:52)
-> /workspace/node_modules/@grpc/grpc-js/src/client.ts:358:36
at Object.onReceiveStatus (node_modules/@grpc/grpc-js/build/src/client-interceptors.js:365:141)
-> /workspace/node_modules/@grpc/grpc-js/src/client-interceptors.ts:462:34
at Object.onReceiveStatus (node_modules/@grpc/grpc-js/build/src/client-interceptors.js:328:181)
-> /workspace/node_modules/@grpc/grpc-js/src/client-interceptors.ts:424:48
at /workspace/node_modules/@grpc/grpc-js/build/src/call-stream.js:188:78
-> /workspace/node_modules/@grpc/grpc-js/src/call-stream.ts:334:24
at processTicksAndRejections (internal/process/task_queues.js:79:11)
for call at
at ServiceClientImpl.makeUnaryRequest (node_modules/@grpc/grpc-js/build/src/client.js:163:34)
-> /workspace/node_modules/@grpc/grpc-js/src/client.ts:328:30
at ServiceClientImpl.<anonymous> (node_modules/@grpc/grpc-js/build/src/make-client.js:105:19)
-> /workspace/node_modules/@grpc/grpc-js/src/make-client.ts:189:15
at /workspace/build/src/v1/datastore_admin_client.js:294:29
-> /workspace/src/v1/datastore_admin_client.ts:392:25
at /workspace/node_modules/google-gax/build/src/normalCalls/timeout.js:44:16
-> /workspace/node_modules/google-gax/src/normalCalls/timeout.ts:54:13
at LongrunningApiCaller._wrapOperation (node_modules/google-gax/build/src/longRunningCalls/longRunningApiCaller.js:55:16)
-> /workspace/node_modules/google-gax/src/longRunningCalls/longRunningApiCaller.ts:80:12
at /workspace/node_modules/google-gax/build/src/longRunningCalls/longRunningApiCaller.js:46:25
-> /workspace/node_modules/google-gax/src/longRunningCalls/longRunningApiCaller.ts:64:19
at OngoingCall.call (node_modules/google-gax/build/src/call.js:67:27)
-> /workspace/node_modules/google-gax/src/call.ts:81:23
at LongrunningApiCaller.call (node_modules/google-gax/build/src/longRunningCalls/longRunningApiCaller.js:45:19)
-> /workspace/node_modules/google-gax/src/longRunningCalls/longRunningApiCaller.ts:63:15
at /workspace/node_modules/google-gax/build/src/createApiCall.js:84:30
-> /workspace/node_modules/google-gax/src/createApiCall.ts:118:26
at processTicksAndRejections (internal/process/task_queues.js:97:5)</pre></details> | 1.0 | Datastore importing and exporting entities: should export, then import entities failed - Note: #996 was also for this test, but it was closed more than 10 days ago. So, I didn't mark it flaky.
----
commit: 465c6cadee9f534b4c29e746674535f00f586390
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/3e2b8e61-ed9d-4602-96d2-243de5c47c46), [Sponge](http://sponge2/3e2b8e61-ed9d-4602-96d2-243de5c47c46)
status: failed
<details><summary>Test output</summary><br><pre>16 UNAUTHENTICATED: Request had invalid authentication credentials. Expected OAuth 2 access token, login cookie or other valid authentication credential. See https://developers.google.com/identity/sign-in/web/devconsole-project.
Error: 16 UNAUTHENTICATED: Request had invalid authentication credentials. Expected OAuth 2 access token, login cookie or other valid authentication credential. See https://developers.google.com/identity/sign-in/web/devconsole-project.
at Object.callErrorFromStatus (node_modules/@grpc/grpc-js/build/src/call.js:31:19)
-> /workspace/node_modules/@grpc/grpc-js/src/call.ts:81:17
at Object.onReceiveStatus (node_modules/@grpc/grpc-js/build/src/client.js:195:52)
-> /workspace/node_modules/@grpc/grpc-js/src/client.ts:358:36
at Object.onReceiveStatus (node_modules/@grpc/grpc-js/build/src/client-interceptors.js:365:141)
-> /workspace/node_modules/@grpc/grpc-js/src/client-interceptors.ts:462:34
at Object.onReceiveStatus (node_modules/@grpc/grpc-js/build/src/client-interceptors.js:328:181)
-> /workspace/node_modules/@grpc/grpc-js/src/client-interceptors.ts:424:48
at /workspace/node_modules/@grpc/grpc-js/build/src/call-stream.js:188:78
-> /workspace/node_modules/@grpc/grpc-js/src/call-stream.ts:334:24
at processTicksAndRejections (internal/process/task_queues.js:79:11)
for call at
at ServiceClientImpl.makeUnaryRequest (node_modules/@grpc/grpc-js/build/src/client.js:163:34)
-> /workspace/node_modules/@grpc/grpc-js/src/client.ts:328:30
at ServiceClientImpl.<anonymous> (node_modules/@grpc/grpc-js/build/src/make-client.js:105:19)
-> /workspace/node_modules/@grpc/grpc-js/src/make-client.ts:189:15
at /workspace/build/src/v1/datastore_admin_client.js:294:29
-> /workspace/src/v1/datastore_admin_client.ts:392:25
at /workspace/node_modules/google-gax/build/src/normalCalls/timeout.js:44:16
-> /workspace/node_modules/google-gax/src/normalCalls/timeout.ts:54:13
at LongrunningApiCaller._wrapOperation (node_modules/google-gax/build/src/longRunningCalls/longRunningApiCaller.js:55:16)
-> /workspace/node_modules/google-gax/src/longRunningCalls/longRunningApiCaller.ts:80:12
at /workspace/node_modules/google-gax/build/src/longRunningCalls/longRunningApiCaller.js:46:25
-> /workspace/node_modules/google-gax/src/longRunningCalls/longRunningApiCaller.ts:64:19
at OngoingCall.call (node_modules/google-gax/build/src/call.js:67:27)
-> /workspace/node_modules/google-gax/src/call.ts:81:23
at LongrunningApiCaller.call (node_modules/google-gax/build/src/longRunningCalls/longRunningApiCaller.js:45:19)
-> /workspace/node_modules/google-gax/src/longRunningCalls/longRunningApiCaller.ts:63:15
at /workspace/node_modules/google-gax/build/src/createApiCall.js:84:30
-> /workspace/node_modules/google-gax/src/createApiCall.ts:118:26
at processTicksAndRejections (internal/process/task_queues.js:97:5)</pre></details> | non_defect | datastore importing and exporting entities should export then import entities failed note was also for this test but it was closed more than days ago so i didn t mark it flaky commit buildurl status failed test output unauthenticated request had invalid authentication credentials expected oauth access token login cookie or other valid authentication credential see error unauthenticated request had invalid authentication credentials expected oauth access token login cookie or other valid authentication credential see at object callerrorfromstatus node modules grpc grpc js build src call js workspace node modules grpc grpc js src call ts at object onreceivestatus node modules grpc grpc js build src client js workspace node modules grpc grpc js src client ts at object onreceivestatus node modules grpc grpc js build src client interceptors js workspace node modules grpc grpc js src client interceptors ts at object onreceivestatus node modules grpc grpc js build src client interceptors js workspace node modules grpc grpc js src client interceptors ts at workspace node modules grpc grpc js build src call stream js workspace node modules grpc grpc js src call stream ts at processticksandrejections internal process task queues js for call at at serviceclientimpl makeunaryrequest node modules grpc grpc js build src client js workspace node modules grpc grpc js src client ts at serviceclientimpl node modules grpc grpc js build src make client js workspace node modules grpc grpc js src make client ts at workspace build src datastore admin client js workspace src datastore admin client ts at workspace node modules google gax build src normalcalls timeout js workspace node modules google gax src normalcalls timeout ts at longrunningapicaller wrapoperation node modules google gax build src longrunningcalls longrunningapicaller js workspace node modules google gax src longrunningcalls longrunningapicaller ts at workspace node modules google gax build src longrunningcalls longrunningapicaller js workspace node modules google gax src longrunningcalls longrunningapicaller ts at ongoingcall call node modules google gax build src call js workspace node modules google gax src call ts at longrunningapicaller call node modules google gax build src longrunningcalls longrunningapicaller js workspace node modules google gax src longrunningcalls longrunningapicaller ts at workspace node modules google gax build src createapicall js workspace node modules google gax src createapicall ts at processticksandrejections internal process task queues js | 0 |
62,060 | 7,545,314,911 | IssuesEvent | 2018-04-17 21:12:47 | Microsoft/TypeScript | https://api.github.com/repos/Microsoft/TypeScript | closed | Suggestion Backlog Slog, 4/16/2018 | Design Notes | The "Ryan is optimistic about our pace" edition
* #23405 Support non-null assertion operator in JSDoc
* #23393 Collapse multiple error reports in `--pretty`
* #23340 Warn for excess properties in spreaded object literal
* #23305 Enforce never-initialized varibles / `strictVariableInitialization`
* #23274 Type guards by `expr.constructor` (sameish as `instanceof`)
* #23226 `isObjectTypeWithInferableIndex` returns `false` for intersection type with index signature
* #23188 Locally-scoped type aliases
* #23132 Improve behavior of conditional types instantiated with constrained generics
* #23005 `T[K]` should be `never` when `K` is `never`
* #22892 `string` `enum` object should be indexable type
* #22851 `esModuleInterop` should work when `target` = `esnext`
* #22815 Abstract classes that implement interfaces shouldn't require method signatures
* #22806 `Partial<T>` should be a weak type
* #22769 Allow unshadowed parameter initializer references in ES6+
* #22759 Let JSX children be subject to tupleness
* #22709 Allow references to literal-ish-initialized enums in type positions
* #22669 Add a new overload to `Function#bind`
* #22665 Add a mode to make TS act like JS
* #22631 Allow named type parameter arguments
* #22649 Combine tsconfig with file list
* #22610 Keep `infer` variable in scope in false arm of conditional type
* #22609 Do some type guards based on overload when a good discriminant is present
* #22605 Provide a back-compat mechanism for bundled .d.ts files in package.json
* #22598 Allow speculative union type property access in `typeof` (expression) operands
* #22509 Something something mapped types
* #22311 Error on out-of-scope *literal* assigned to enum
* #22230 Allow implicit `undefined`->`0` coercion under `strictNullChecks` for bitwise ops
* #22208 Prefer .d.ts over .ts if it's in `files` array
| 1.0 | Suggestion Backlog Slog, 4/16/2018 - The "Ryan is optimistic about our pace" edition
* #23405 Support non-null assertion operator in JSDoc
* #23393 Collapse multiple error reports in `--pretty`
* #23340 Warn for excess properties in spreaded object literal
* #23305 Enforce never-initialized varibles / `strictVariableInitialization`
* #23274 Type guards by `expr.constructor` (sameish as `instanceof`)
* #23226 `isObjectTypeWithInferableIndex` returns `false` for intersection type with index signature
* #23188 Locally-scoped type aliases
* #23132 Improve behavior of conditional types instantiated with constrained generics
* #23005 `T[K]` should be `never` when `K` is `never`
* #22892 `string` `enum` object should be indexable type
* #22851 `esModuleInterop` should work when `target` = `esnext`
* #22815 Abstract classes that implement interfaces shouldn't require method signatures
* #22806 `Partial<T>` should be a weak type
* #22769 Allow unshadowed parameter initializer references in ES6+
* #22759 Let JSX children be subject to tupleness
* #22709 Allow references to literal-ish-initialized enums in type positions
* #22669 Add a new overload to `Function#bind`
* #22665 Add a mode to make TS act like JS
* #22631 Allow named type parameter arguments
* #22649 Combine tsconfig with file list
* #22610 Keep `infer` variable in scope in false arm of conditional type
* #22609 Do some type guards based on overload when a good discriminant is present
* #22605 Provide a back-compat mechanism for bundled .d.ts files in package.json
* #22598 Allow speculative union type property access in `typeof` (expression) operands
* #22509 Something something mapped types
* #22311 Error on out-of-scope *literal* assigned to enum
* #22230 Allow implicit `undefined`->`0` coercion under `strictNullChecks` for bitwise ops
* #22208 Prefer .d.ts over .ts if it's in `files` array
| non_defect | suggestion backlog slog the ryan is optimistic about our pace edition support non null assertion operator in jsdoc collapse multiple error reports in pretty warn for excess properties in spreaded object literal enforce never initialized varibles strictvariableinitialization type guards by expr constructor sameish as instanceof isobjecttypewithinferableindex returns false for intersection type with index signature locally scoped type aliases improve behavior of conditional types instantiated with constrained generics t should be never when k is never string enum object should be indexable type esmoduleinterop should work when target esnext abstract classes that implement interfaces shouldn t require method signatures partial should be a weak type allow unshadowed parameter initializer references in let jsx children be subject to tupleness allow references to literal ish initialized enums in type positions add a new overload to function bind add a mode to make ts act like js allow named type parameter arguments combine tsconfig with file list keep infer variable in scope in false arm of conditional type do some type guards based on overload when a good discriminant is present provide a back compat mechanism for bundled d ts files in package json allow speculative union type property access in typeof expression operands something something mapped types error on out of scope literal assigned to enum allow implicit undefined coercion under strictnullchecks for bitwise ops prefer d ts over ts if it s in files array | 0 |
11,278 | 2,648,771,644 | IssuesEvent | 2015-03-14 07:28:41 | pyroscope/pyroscope | https://api.github.com/repos/pyroscope/pyroscope | closed | build.sh Fails on OS X | auto-migrated Priority-Medium Type-Defect | ```
What steps will reproduce the problem?
1. Running build.sh
What is the expected output? What do you see instead?
I'm trying to build rtorrent-extended on Mac OS X (Lion). When I run build.sh
all it seems to complete the build of rtorrent-vanilla (with a bunch of
errors), but is unable to compile rtorrent-extended.
It fails with: ready to configure
./configure: line 16813: syntax error near unexpected token `RT_HEX_VERSION,'
./configure: line 16813: `nAC_DEFINE(RT_HEX_VERSION, 0x000809, for CPP if
checks)nAC_DEFINE(API_VERSION, 0, api version)'
What version of the product are you using? On what operating system?
I'm compiling from svn on Mac OS X 10.7.3
Please provide any additional information below.
To get build.sh to run at all I had to change libtool to glibtool in the first
place.
```
Original issue reported on code.google.com by `deseptic...@gmail.com` on 6 May 2012 at 4:25 | 1.0 | build.sh Fails on OS X - ```
What steps will reproduce the problem?
1. Running build.sh
What is the expected output? What do you see instead?
I'm trying to build rtorrent-extended on Mac OS X (Lion). When I run build.sh
all it seems to complete the build of rtorrent-vanilla (with a bunch of
errors), but is unable to compile rtorrent-extended.
It fails with: ready to configure
./configure: line 16813: syntax error near unexpected token `RT_HEX_VERSION,'
./configure: line 16813: `nAC_DEFINE(RT_HEX_VERSION, 0x000809, for CPP if
checks)nAC_DEFINE(API_VERSION, 0, api version)'
What version of the product are you using? On what operating system?
I'm compiling from svn on Mac OS X 10.7.3
Please provide any additional information below.
To get build.sh to run at all I had to change libtool to glibtool in the first
place.
```
Original issue reported on code.google.com by `deseptic...@gmail.com` on 6 May 2012 at 4:25 | defect | build sh fails on os x what steps will reproduce the problem running build sh what is the expected output what do you see instead i m trying to build rtorrent extended on mac os x lion when i run build sh all it seems to complete the build of rtorrent vanilla with a bunch of errors but is unable to compile rtorrent extended it fails with ready to configure configure line syntax error near unexpected token rt hex version configure line nac define rt hex version for cpp if checks nac define api version api version what version of the product are you using on what operating system i m compiling from svn on mac os x please provide any additional information below to get build sh to run at all i had to change libtool to glibtool in the first place original issue reported on code google com by deseptic gmail com on may at | 1 |
35,937 | 12,394,503,193 | IssuesEvent | 2020-05-20 17:02:37 | rammatzkvosky/123456 | https://api.github.com/repos/rammatzkvosky/123456 | closed | CVE-2014-3568 (Medium) detected in io.js, openssl-OpenSSL_1_0_1 | security vulnerability | ## CVE-2014-3568 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - </p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
OpenSSL before 0.9.8zc, 1.0.0 before 1.0.0o, and 1.0.1 before 1.0.1j does not properly enforce the no-ssl3 build option, which allows remote attackers to bypass intended access restrictions via an SSL 3.0 handshake, related to s23_clnt.c and s23_srvr.c.
<p>Publish Date: 2014-10-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-3568>CVE-2014-3568</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2014-3568">https://nvd.nist.gov/vuln/detail/CVE-2014-3568</a></p>
<p>Release Date: 2014-10-19</p>
<p>Fix Resolution: 0.9.8zc,1.0.0o,1.0.1j</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"vulnerabilityIdentifier":"CVE-2014-3568","vulnerabilityDetails":"OpenSSL before 0.9.8zc, 1.0.0 before 1.0.0o, and 1.0.1 before 1.0.1j does not properly enforce the no-ssl3 build option, which allows remote attackers to bypass intended access restrictions via an SSL 3.0 handshake, related to s23_clnt.c and s23_srvr.c.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-3568","cvss2Severity":"medium","cvss2Score":"4.3","extraData":{}}</REMEDIATE> --> | True | CVE-2014-3568 (Medium) detected in io.js, openssl-OpenSSL_1_0_1 - ## CVE-2014-3568 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - </p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
OpenSSL before 0.9.8zc, 1.0.0 before 1.0.0o, and 1.0.1 before 1.0.1j does not properly enforce the no-ssl3 build option, which allows remote attackers to bypass intended access restrictions via an SSL 3.0 handshake, related to s23_clnt.c and s23_srvr.c.
<p>Publish Date: 2014-10-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-3568>CVE-2014-3568</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2014-3568">https://nvd.nist.gov/vuln/detail/CVE-2014-3568</a></p>
<p>Release Date: 2014-10-19</p>
<p>Fix Resolution: 0.9.8zc,1.0.0o,1.0.1j</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"vulnerabilityIdentifier":"CVE-2014-3568","vulnerabilityDetails":"OpenSSL before 0.9.8zc, 1.0.0 before 1.0.0o, and 1.0.1 before 1.0.1j does not properly enforce the no-ssl3 build option, which allows remote attackers to bypass intended access restrictions via an SSL 3.0 handshake, related to s23_clnt.c and s23_srvr.c.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-3568","cvss2Severity":"medium","cvss2Score":"4.3","extraData":{}}</REMEDIATE> --> | non_defect | cve medium detected in io js openssl openssl cve medium severity vulnerability vulnerable libraries vulnerability details openssl before before and before does not properly enforce the no build option which allows remote attackers to bypass intended access restrictions via an ssl handshake related to clnt c and srvr c publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails openssl before before and before does not properly enforce the no build option which allows remote attackers to bypass intended access restrictions via an ssl handshake related to clnt c and srvr c vulnerabilityurl | 0 |
4,960 | 6,953,365,555 | IssuesEvent | 2017-12-06 20:45:45 | kubernetes/kubernetes | https://api.github.com/repos/kubernetes/kubernetes | closed | Kubernetes Network Policy | sig/network sig/service-catalog team/cluster (deprecated - do not use) | Raising this issue to track the status of network policy in Kubernetes so it isn't hidden within the network SIG.
Current rough plan:
- [x] Short-term: Define v1alpha1 network policy using API extensions.
- [x] Medium-term [v1.3]: Implement as Kubernetes v1beta API object. (#25638)
- [x] Medium-term: Refine and add to API based on user-feedback.
- [x] Long-term: Implement as first-class API in k8s.
v1beta API is outlined here: https://github.com/kubernetes/kubernetes/pull/24154/files
and here: https://docs.google.com/document/d/1qAm-_oSap-f1d6a-xRTj6xaH1sYQBfK36VyjB5XOZug/edit
Some future considerations and discussion points:
- [x] Egress (outgoing) network policy
- [x] External policy (from outside the cluster)
- [ ] How does policy fit in to multi-tenancy model?
- [ ] Further policing cross-namespace connectivity (e.g allow from these labels in these namespaces).
| 1.0 | Kubernetes Network Policy - Raising this issue to track the status of network policy in Kubernetes so it isn't hidden within the network SIG.
Current rough plan:
- [x] Short-term: Define v1alpha1 network policy using API extensions.
- [x] Medium-term [v1.3]: Implement as Kubernetes v1beta API object. (#25638)
- [x] Medium-term: Refine and add to API based on user-feedback.
- [x] Long-term: Implement as first-class API in k8s.
v1beta API is outlined here: https://github.com/kubernetes/kubernetes/pull/24154/files
and here: https://docs.google.com/document/d/1qAm-_oSap-f1d6a-xRTj6xaH1sYQBfK36VyjB5XOZug/edit
Some future considerations and discussion points:
- [x] Egress (outgoing) network policy
- [x] External policy (from outside the cluster)
- [ ] How does policy fit in to multi-tenancy model?
- [ ] Further policing cross-namespace connectivity (e.g allow from these labels in these namespaces).
| non_defect | kubernetes network policy raising this issue to track the status of network policy in kubernetes so it isn t hidden within the network sig current rough plan short term define network policy using api extensions medium term implement as kubernetes api object medium term refine and add to api based on user feedback long term implement as first class api in api is outlined here and here some future considerations and discussion points egress outgoing network policy external policy from outside the cluster how does policy fit in to multi tenancy model further policing cross namespace connectivity e g allow from these labels in these namespaces | 0 |
65,192 | 19,254,272,901 | IssuesEvent | 2021-12-09 09:36:57 | openzfs/zfs | https://api.github.com/repos/openzfs/zfs | closed | `zfs upgrade` feasts on your free space | Type: Defect | ### System information
<!-- add version after "|" character -->
Type | Version/Name
--- | ---
Distribution Name | Debian
Distribution Version | 11
Kernel Version | 5.10.0-9-amd64
Architecture | x86_64
OpenZFS Version | 9699e45d5
### Describe the problem you're observing
While trying to reproduce #11679 using the instructions in the illumos bug, I produced a v3 dataset on a v14 pool, by using a script I wrote to replay filesystem histories onto new datasets for testing various things, on a dataset that's USED/LUSED 25/50 GB as-is.
One `zfs send -R | ... | zfs recv -x encryption newpool/encroot/olddata` later, I had taken up 25 GB of a 40 GB pool. I then did a number of `zfs clone newpool/encroot/olddata@somesnap`, which curiously triggered eating a couple more GB incrementally.
Then I ran `zfs upgrade -a`, and of the ~8 GB free, 0 bytes remained, after a little while. And if I destroyed one of the clones, it freed a GB or so, which promptly got eaten in short order.
Curiously, I then tried expanding the vdev by 8 GB (truncate -s 48G newpoolfile;zpool reopen newpool; zpool online -e newpool), and found that it only eats free space up to the amount the pool had before I did the online -e - it will feast on the free space again if I destroy the clones+rollback to an older snapshot then do it again, but always only up to 40 GB.
### Describe how to reproduce the problem
As above.
### Include any warning/errors/backtraces from the system logs
Nothing, though on another round of trying this, I got #11490 to come out. | 1.0 | `zfs upgrade` feasts on your free space - ### System information
<!-- add version after "|" character -->
Type | Version/Name
--- | ---
Distribution Name | Debian
Distribution Version | 11
Kernel Version | 5.10.0-9-amd64
Architecture | x86_64
OpenZFS Version | 9699e45d5
### Describe the problem you're observing
While trying to reproduce #11679 using the instructions in the illumos bug, I produced a v3 dataset on a v14 pool, by using a script I wrote to replay filesystem histories onto new datasets for testing various things, on a dataset that's USED/LUSED 25/50 GB as-is.
One `zfs send -R | ... | zfs recv -x encryption newpool/encroot/olddata` later, I had taken up 25 GB of a 40 GB pool. I then did a number of `zfs clone newpool/encroot/olddata@somesnap`, which curiously triggered eating a couple more GB incrementally.
Then I ran `zfs upgrade -a`, and of the ~8 GB free, 0 bytes remained, after a little while. And if I destroyed one of the clones, it freed a GB or so, which promptly got eaten in short order.
Curiously, I then tried expanding the vdev by 8 GB (truncate -s 48G newpoolfile;zpool reopen newpool; zpool online -e newpool), and found that it only eats free space up to the amount the pool had before I did the online -e - it will feast on the free space again if I destroy the clones+rollback to an older snapshot then do it again, but always only up to 40 GB.
### Describe how to reproduce the problem
As above.
### Include any warning/errors/backtraces from the system logs
Nothing, though on another round of trying this, I got #11490 to come out. | defect | zfs upgrade feasts on your free space system information type version name distribution name debian distribution version kernel version architecture openzfs version describe the problem you re observing while trying to reproduce using the instructions in the illumos bug i produced a dataset on a pool by using a script i wrote to replay filesystem histories onto new datasets for testing various things on a dataset that s used lused gb as is one zfs send r zfs recv x encryption newpool encroot olddata later i had taken up gb of a gb pool i then did a number of zfs clone newpool encroot olddata somesnap which curiously triggered eating a couple more gb incrementally then i ran zfs upgrade a and of the gb free bytes remained after a little while and if i destroyed one of the clones it freed a gb or so which promptly got eaten in short order curiously i then tried expanding the vdev by gb truncate s newpoolfile zpool reopen newpool zpool online e newpool and found that it only eats free space up to the amount the pool had before i did the online e it will feast on the free space again if i destroy the clones rollback to an older snapshot then do it again but always only up to gb describe how to reproduce the problem as above include any warning errors backtraces from the system logs nothing though on another round of trying this i got to come out | 1 |
47,908 | 13,066,351,738 | IssuesEvent | 2020-07-30 21:30:52 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | closed | steamshovel crash reproducibility (Trac #1392) | Migrated from Trac combo core defect | It seems there is a simple way to provoke the steamshovel crash:
- Add Bubbles (not ChargeBubbles)
- Pick pulses (e.g. OfflineIceTopVEMPulses)
- Remove bubbles
- Program received signal SIGSEGV, Segmentation fault.
(gdb) bt
https://code.icecube.wisc.edu/ticket/0 0x00007ffff3884241 in ?? () from /usr/lib/x86_64-linux-gnu/libpython2.7.so.1.0
#1 0x00007ffff53be552 in boost::python::converter::shared_ptr_deleter::operator()(void const*) ()
from /home/berghaus/i3/ports/lib/boost-1.38.0/libboost_python-mt.so
#2 0x00007ffff1258842 in SphereObject::~SphereObject() ()
from /home/berghaus/icerec/build/lib/libshovelart.so
#3 0x00007ffff1261456 in SceneGroup::~SceneGroup() ()
from /home/berghaus/icerec/build/lib/libshovelart.so
#4 0x00007ffff1261509 in SceneGroup::~SceneGroup() ()
from /home/berghaus/icerec/build/lib/libshovelart.so
#5 0x00000000004bbbb2 in std::_Rb_tree<boost::shared_ptr<SceneGroup>, boost::shared_ptr<SceneGroup>, std::_Identity<boost::shared_ptr<SceneGroup> >, std::less<boost::shared_ptr<SceneGroup> >, std::allocator<boost::shared_ptr<SceneGroup> > >::_M_erase(std::_Rb_tree_node<boost::shared_ptr<SceneGroup> >*) ()
#6 0x00007ffff1262b39 in Scene::dropOutputs(boost::shared_ptr<Artist>) ()
from /home/berghaus/icerec/build/lib/libshovelart.so
#7 0x00007ffff1263709 in Scene::dropSource(boost::shared_ptr<Artist>) ()
from /home/berghaus/icerec/build/lib/libshovelart.so
#8 0x00007ffff126ad04 in Scenario::remove(boost::shared_ptr<Artist>) ()
from /home/berghaus/icerec/build/lib/libshovelart.so
#9 0x00000000004c5692 in ScenarioWidget::removeSelection() ()
Migrated from https://code.icecube.wisc.edu/ticket/1392
```json
{
"status": "closed",
"changetime": "2015-10-14T15:47:25",
"description": "It seems there is a simple way to provoke the steamshovel crash:\n\n- Add Bubbles (not ChargeBubbles)\n- Pick pulses (e.g. OfflineIceTopVEMPulses)\n- Remove bubbles\n- Program received signal SIGSEGV, Segmentation fault.\n\n(gdb) bt\n#0 0x00007ffff3884241 in ?? () from /usr/lib/x86_64-linux-gnu/libpython2.7.so.1.0\n#1 0x00007ffff53be552 in boost::python::converter::shared_ptr_deleter::operator()(void const*) ()\n from /home/berghaus/i3/ports/lib/boost-1.38.0/libboost_python-mt.so\n#2 0x00007ffff1258842 in SphereObject::~SphereObject() ()\n from /home/berghaus/icerec/build/lib/libshovelart.so\n#3 0x00007ffff1261456 in SceneGroup::~SceneGroup() ()\n from /home/berghaus/icerec/build/lib/libshovelart.so\n#4 0x00007ffff1261509 in SceneGroup::~SceneGroup() ()\n from /home/berghaus/icerec/build/lib/libshovelart.so\n#5 0x00000000004bbbb2 in std::_Rb_tree<boost::shared_ptr<SceneGroup>, boost::shared_ptr<SceneGroup>, std::_Identity<boost::shared_ptr<SceneGroup> >, std::less<boost::shared_ptr<SceneGroup> >, std::allocator<boost::shared_ptr<SceneGroup> > >::_M_erase(std::_Rb_tree_node<boost::shared_ptr<SceneGroup> >*) ()\n#6 0x00007ffff1262b39 in Scene::dropOutputs(boost::shared_ptr<Artist>) ()\n from /home/berghaus/icerec/build/lib/libshovelart.so\n#7 0x00007ffff1263709 in Scene::dropSource(boost::shared_ptr<Artist>) ()\n from /home/berghaus/icerec/build/lib/libshovelart.so\n#8 0x00007ffff126ad04 in Scenario::remove(boost::shared_ptr<Artist>) ()\n from /home/berghaus/icerec/build/lib/libshovelart.so\n#9 0x00000000004c5692 in ScenarioWidget::removeSelection() ()\n",
"reporter": "berghaus",
"cc": "",
"resolution": "worksforme",
"_ts": "1444837645884416",
"component": "combo core",
"summary": "steamshovel crash reproducibility",
"priority": "minor",
"keywords": "steamshovel",
"time": "2015-10-09T12:52:41",
"milestone": "",
"owner": "hdembinski",
"type": "defect"
}
```
| 1.0 | steamshovel crash reproducibility (Trac #1392) - It seems there is a simple way to provoke the steamshovel crash:
- Add Bubbles (not ChargeBubbles)
- Pick pulses (e.g. OfflineIceTopVEMPulses)
- Remove bubbles
- Program received signal SIGSEGV, Segmentation fault.
(gdb) bt
https://code.icecube.wisc.edu/ticket/0 0x00007ffff3884241 in ?? () from /usr/lib/x86_64-linux-gnu/libpython2.7.so.1.0
#1 0x00007ffff53be552 in boost::python::converter::shared_ptr_deleter::operator()(void const*) ()
from /home/berghaus/i3/ports/lib/boost-1.38.0/libboost_python-mt.so
#2 0x00007ffff1258842 in SphereObject::~SphereObject() ()
from /home/berghaus/icerec/build/lib/libshovelart.so
#3 0x00007ffff1261456 in SceneGroup::~SceneGroup() ()
from /home/berghaus/icerec/build/lib/libshovelart.so
#4 0x00007ffff1261509 in SceneGroup::~SceneGroup() ()
from /home/berghaus/icerec/build/lib/libshovelart.so
#5 0x00000000004bbbb2 in std::_Rb_tree<boost::shared_ptr<SceneGroup>, boost::shared_ptr<SceneGroup>, std::_Identity<boost::shared_ptr<SceneGroup> >, std::less<boost::shared_ptr<SceneGroup> >, std::allocator<boost::shared_ptr<SceneGroup> > >::_M_erase(std::_Rb_tree_node<boost::shared_ptr<SceneGroup> >*) ()
#6 0x00007ffff1262b39 in Scene::dropOutputs(boost::shared_ptr<Artist>) ()
from /home/berghaus/icerec/build/lib/libshovelart.so
#7 0x00007ffff1263709 in Scene::dropSource(boost::shared_ptr<Artist>) ()
from /home/berghaus/icerec/build/lib/libshovelart.so
#8 0x00007ffff126ad04 in Scenario::remove(boost::shared_ptr<Artist>) ()
from /home/berghaus/icerec/build/lib/libshovelart.so
#9 0x00000000004c5692 in ScenarioWidget::removeSelection() ()
Migrated from https://code.icecube.wisc.edu/ticket/1392
```json
{
"status": "closed",
"changetime": "2015-10-14T15:47:25",
"description": "It seems there is a simple way to provoke the steamshovel crash:\n\n- Add Bubbles (not ChargeBubbles)\n- Pick pulses (e.g. OfflineIceTopVEMPulses)\n- Remove bubbles\n- Program received signal SIGSEGV, Segmentation fault.\n\n(gdb) bt\n#0 0x00007ffff3884241 in ?? () from /usr/lib/x86_64-linux-gnu/libpython2.7.so.1.0\n#1 0x00007ffff53be552 in boost::python::converter::shared_ptr_deleter::operator()(void const*) ()\n from /home/berghaus/i3/ports/lib/boost-1.38.0/libboost_python-mt.so\n#2 0x00007ffff1258842 in SphereObject::~SphereObject() ()\n from /home/berghaus/icerec/build/lib/libshovelart.so\n#3 0x00007ffff1261456 in SceneGroup::~SceneGroup() ()\n from /home/berghaus/icerec/build/lib/libshovelart.so\n#4 0x00007ffff1261509 in SceneGroup::~SceneGroup() ()\n from /home/berghaus/icerec/build/lib/libshovelart.so\n#5 0x00000000004bbbb2 in std::_Rb_tree<boost::shared_ptr<SceneGroup>, boost::shared_ptr<SceneGroup>, std::_Identity<boost::shared_ptr<SceneGroup> >, std::less<boost::shared_ptr<SceneGroup> >, std::allocator<boost::shared_ptr<SceneGroup> > >::_M_erase(std::_Rb_tree_node<boost::shared_ptr<SceneGroup> >*) ()\n#6 0x00007ffff1262b39 in Scene::dropOutputs(boost::shared_ptr<Artist>) ()\n from /home/berghaus/icerec/build/lib/libshovelart.so\n#7 0x00007ffff1263709 in Scene::dropSource(boost::shared_ptr<Artist>) ()\n from /home/berghaus/icerec/build/lib/libshovelart.so\n#8 0x00007ffff126ad04 in Scenario::remove(boost::shared_ptr<Artist>) ()\n from /home/berghaus/icerec/build/lib/libshovelart.so\n#9 0x00000000004c5692 in ScenarioWidget::removeSelection() ()\n",
"reporter": "berghaus",
"cc": "",
"resolution": "worksforme",
"_ts": "1444837645884416",
"component": "combo core",
"summary": "steamshovel crash reproducibility",
"priority": "minor",
"keywords": "steamshovel",
"time": "2015-10-09T12:52:41",
"milestone": "",
"owner": "hdembinski",
"type": "defect"
}
```
| defect | steamshovel crash reproducibility trac it seems there is a simple way to provoke the steamshovel crash add bubbles not chargebubbles pick pulses e g offlineicetopvempulses remove bubbles program received signal sigsegv segmentation fault gdb bt in from usr lib linux gnu so in boost python converter shared ptr deleter operator void const from home berghaus ports lib boost libboost python mt so in sphereobject sphereobject from home berghaus icerec build lib libshovelart so in scenegroup scenegroup from home berghaus icerec build lib libshovelart so in scenegroup scenegroup from home berghaus icerec build lib libshovelart so in std rb tree boost shared ptr std identity std less std allocator m erase std rb tree node in scene dropoutputs boost shared ptr from home berghaus icerec build lib libshovelart so in scene dropsource boost shared ptr from home berghaus icerec build lib libshovelart so in scenario remove boost shared ptr from home berghaus icerec build lib libshovelart so in scenariowidget removeselection migrated from json status closed changetime description it seems there is a simple way to provoke the steamshovel crash n n add bubbles not chargebubbles n pick pulses e g offlineicetopvempulses n remove bubbles n program received signal sigsegv segmentation fault n n gdb bt n in from usr lib linux gnu so n in boost python converter shared ptr deleter operator void const n from home berghaus ports lib boost libboost python mt so n in sphereobject sphereobject n from home berghaus icerec build lib libshovelart so n in scenegroup scenegroup n from home berghaus icerec build lib libshovelart so n in scenegroup scenegroup n from home berghaus icerec build lib libshovelart so n in std rb tree boost shared ptr std identity std less std allocator m erase std rb tree node n in scene dropoutputs boost shared ptr n from home berghaus icerec build lib libshovelart so n in scene dropsource boost shared ptr n from home berghaus icerec build lib libshovelart so n in scenario remove boost shared ptr n from home berghaus icerec build lib libshovelart so n in scenariowidget removeselection n reporter berghaus cc resolution worksforme ts component combo core summary steamshovel crash reproducibility priority minor keywords steamshovel time milestone owner hdembinski type defect | 1 |
3,042 | 2,607,970,226 | IssuesEvent | 2015-02-26 00:44:14 | chrsmithdemos/leveldb | https://api.github.com/repos/chrsmithdemos/leveldb | opened | BloomFilterPolicy not interoperable between ARM and x86 | auto-migrated Priority-Medium Type-Defect | ```
We've been struggling with an elusive issue for a while in which LevelDB
database files were not compatible between platforms. Copied databases were
failing in subtle ways undetected by any checks.
After a slough of debugging this was narrowed down to use of BloomFilterPolicy.
The bloom filter uses the Hash function that can return different output based
on char signedness. To be specific: if the number of characters is not a
multiple of four, and at least one of the trailing characters is >0x80.
Attached is a patch that:
- Add casts to Hash() to treat chars as unsigned (I think this was intended)
- Adds tests for Hash
- Change name of algoritm in BloomFilterPolicy::Name to make sure that
filters are recomputed; this provides forward and backward compatibility
Luckily, the use of Hash() in BloomFilterPolicy seems to be the only place
where the result of that function affects what is written to disk.
```
-----
Original issue reported on code.google.com by `laa...@gmail.com` on 7 Jun 2014 at 11:51
Attachments:
* [0001-Make-Hash-independent-of-char-signedness.patch](https://storage.googleapis.com/google-code-attachments/leveldb/issue-237/comment-0/0001-Make-Hash-independent-of-char-signedness.patch)
| 1.0 | BloomFilterPolicy not interoperable between ARM and x86 - ```
We've been struggling with an elusive issue for a while in which LevelDB
database files were not compatible between platforms. Copied databases were
failing in subtle ways undetected by any checks.
After a slough of debugging this was narrowed down to use of BloomFilterPolicy.
The bloom filter uses the Hash function that can return different output based
on char signedness. To be specific: if the number of characters is not a
multiple of four, and at least one of the trailing characters is >0x80.
Attached is a patch that:
- Add casts to Hash() to treat chars as unsigned (I think this was intended)
- Adds tests for Hash
- Change name of algoritm in BloomFilterPolicy::Name to make sure that
filters are recomputed; this provides forward and backward compatibility
Luckily, the use of Hash() in BloomFilterPolicy seems to be the only place
where the result of that function affects what is written to disk.
```
-----
Original issue reported on code.google.com by `laa...@gmail.com` on 7 Jun 2014 at 11:51
Attachments:
* [0001-Make-Hash-independent-of-char-signedness.patch](https://storage.googleapis.com/google-code-attachments/leveldb/issue-237/comment-0/0001-Make-Hash-independent-of-char-signedness.patch)
| defect | bloomfilterpolicy not interoperable between arm and we ve been struggling with an elusive issue for a while in which leveldb database files were not compatible between platforms copied databases were failing in subtle ways undetected by any checks after a slough of debugging this was narrowed down to use of bloomfilterpolicy the bloom filter uses the hash function that can return different output based on char signedness to be specific if the number of characters is not a multiple of four and at least one of the trailing characters is attached is a patch that add casts to hash to treat chars as unsigned i think this was intended adds tests for hash change name of algoritm in bloomfilterpolicy name to make sure that filters are recomputed this provides forward and backward compatibility luckily the use of hash in bloomfilterpolicy seems to be the only place where the result of that function affects what is written to disk original issue reported on code google com by laa gmail com on jun at attachments | 1 |
1,695 | 2,603,969,678 | IssuesEvent | 2015-02-24 18:59:56 | chrsmith/nishazi6 | https://api.github.com/repos/chrsmith/nishazi6 | opened | 沈阳包皮长水泡怎么治疗 | auto-migrated Priority-Medium Type-Defect | ```
沈阳包皮长水泡怎么治疗〓沈陽軍區政治部醫院性病〓TEL:02
4-31023308〓成立于1946年,68年專注于性傳播疾病的研究和治療�
��位于沈陽市沈河區二緯路32號。是一所與新中國同建立共輝�
��的歷史悠久、設備精良、技術權威、專家云集,是預防、保
健、醫療、科研康復為一體的綜合性醫院。是國家首批公立��
�等部隊醫院、全國首批醫療規范定點單位,是第四軍醫大學�
��東南大學等知名高等院校的教學醫院。曾被中國人民解放軍
空軍后勤部衛生部評為衛生工作先進單位,先后兩次榮立集��
�二等功。
```
-----
Original issue reported on code.google.com by `q964105...@gmail.com` on 4 Jun 2014 at 7:24 | 1.0 | 沈阳包皮长水泡怎么治疗 - ```
沈阳包皮长水泡怎么治疗〓沈陽軍區政治部醫院性病〓TEL:02
4-31023308〓成立于1946年,68年專注于性傳播疾病的研究和治療�
��位于沈陽市沈河區二緯路32號。是一所與新中國同建立共輝�
��的歷史悠久、設備精良、技術權威、專家云集,是預防、保
健、醫療、科研康復為一體的綜合性醫院。是國家首批公立��
�等部隊醫院、全國首批醫療規范定點單位,是第四軍醫大學�
��東南大學等知名高等院校的教學醫院。曾被中國人民解放軍
空軍后勤部衛生部評為衛生工作先進單位,先后兩次榮立集��
�二等功。
```
-----
Original issue reported on code.google.com by `q964105...@gmail.com` on 4 Jun 2014 at 7:24 | defect | 沈阳包皮长水泡怎么治疗 沈阳包皮长水泡怎么治疗〓沈陽軍區政治部醫院性病〓tel: 〓 , � �� 。是一所與新中國同建立共輝� ��的歷史悠久、設備精良、技術權威、專家云集,是預防、保 健、醫療、科研康復為一體的綜合性醫院。是國家首批公立�� �等部隊醫院、全國首批醫療規范定點單位,是第四軍醫大學� ��東南大學等知名高等院校的教學醫院。曾被中國人民解放軍 空軍后勤部衛生部評為衛生工作先進單位,先后兩次榮立集�� �二等功。 original issue reported on code google com by gmail com on jun at | 1 |
57,569 | 15,863,372,154 | IssuesEvent | 2021-04-08 12:45:16 | Ferlab-Ste-Justine/clin-project | https://api.github.com/repos/Ferlab-Ste-Justine/clin-project | closed | Prescription - Afficher le MRN par défaut lorsqu'il n'y en a qu'un seul | Defects | Lorsqu’il y a un seul dossier médical (95% du temps), afficher le numéro par défaut. | 1.0 | Prescription - Afficher le MRN par défaut lorsqu'il n'y en a qu'un seul - Lorsqu’il y a un seul dossier médical (95% du temps), afficher le numéro par défaut. | defect | prescription afficher le mrn par défaut lorsqu il n y en a qu un seul lorsqu’il y a un seul dossier médical du temps afficher le numéro par défaut | 1 |
180,631 | 30,538,080,155 | IssuesEvent | 2023-07-19 18:58:25 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | opened | Create wireframe for how to decrease No's to filing for travel | design ux HCE-Checkin | ## Description
Over half of Veterans are answering No that they don't want to file for travel reimbursement.
[Slack thread](https://dsva.slack.com/archives/C022AC2STBM/p1689787982265009?thread_ts=1687781824.917519&cid=C022AC2STBM)
How can we decrease this number?
There are a variety of reasons why Veterans are saying no:
"I don't think it's clear to all. I just mean self-identification of being eligible for BT is likely a subset of those answering NO for those answering it as "I don't want to submit because I've been rejected before for eligibility reasons". New veterans who aren't clear on eligibility standards existing would not know to self identify. Certainly some are answering NO because they don't want to at that time, as in are checking in "late" and don't want to make themselves checked in even later."
## Tasks
- [ ] Read through the background and potential solutions in the slack thread
- [ ] Review screenshots from VetLink (Ben has them) on how they handled BT requests
- [ ] Pick one or two solutions to create wireframes
- [ ] Get feedback from CIE team
- [ ] Get feedback from anyone else that is needed, platform design, content, Shawn Adams, etc.
- [ ] Finalize wireframes
## AC
- [ ] Wireframes have been reviewed
- [ ] Wireframes finalized
- [ ] Create f/u ticket for FE. Work with Lori on prioritization of where it goes. | 1.0 | Create wireframe for how to decrease No's to filing for travel - ## Description
Over half of Veterans are answering No that they don't want to file for travel reimbursement.
[Slack thread](https://dsva.slack.com/archives/C022AC2STBM/p1689787982265009?thread_ts=1687781824.917519&cid=C022AC2STBM)
How can we decrease this number?
There are a variety of reasons why Veterans are saying no:
"I don't think it's clear to all. I just mean self-identification of being eligible for BT is likely a subset of those answering NO for those answering it as "I don't want to submit because I've been rejected before for eligibility reasons". New veterans who aren't clear on eligibility standards existing would not know to self identify. Certainly some are answering NO because they don't want to at that time, as in are checking in "late" and don't want to make themselves checked in even later."
## Tasks
- [ ] Read through the background and potential solutions in the slack thread
- [ ] Review screenshots from VetLink (Ben has them) on how they handled BT requests
- [ ] Pick one or two solutions to create wireframes
- [ ] Get feedback from CIE team
- [ ] Get feedback from anyone else that is needed, platform design, content, Shawn Adams, etc.
- [ ] Finalize wireframes
## AC
- [ ] Wireframes have been reviewed
- [ ] Wireframes finalized
- [ ] Create f/u ticket for FE. Work with Lori on prioritization of where it goes. | non_defect | create wireframe for how to decrease no s to filing for travel description over half of veterans are answering no that they don t want to file for travel reimbursement how can we decrease this number there are a variety of reasons why veterans are saying no i don t think it s clear to all i just mean self identification of being eligible for bt is likely a subset of those answering no for those answering it as i don t want to submit because i ve been rejected before for eligibility reasons new veterans who aren t clear on eligibility standards existing would not know to self identify certainly some are answering no because they don t want to at that time as in are checking in late and don t want to make themselves checked in even later tasks read through the background and potential solutions in the slack thread review screenshots from vetlink ben has them on how they handled bt requests pick one or two solutions to create wireframes get feedback from cie team get feedback from anyone else that is needed platform design content shawn adams etc finalize wireframes ac wireframes have been reviewed wireframes finalized create f u ticket for fe work with lori on prioritization of where it goes | 0 |
79,114 | 7,696,341,563 | IssuesEvent | 2018-05-18 15:02:13 | atom/atom | https://api.github.com/repos/atom/atom | closed | Flaky tests: line ending selector Status bar tile ... | flaky-test | We've seen the line-ending-selector tests below fail twice in the past week:
https://circleci.com/gh/atom/atom/7475
https://circleci.com/gh/atom/atom/7499
Rebuilding can resolve the failures:
<img width="1065" alt="circleci" src="https://user-images.githubusercontent.com/2988/40060813-7467c768-5825-11e8-8bad-0836c878e6b5.png">
These recent failures are correlated with the recent Electron 2.0 upgrade (#17273), although we've seen these failures before (e.g., https://circleci.com/gh/atom/atom/7267).
### Failures
```
Package tests failed for line-ending-selector:
..........FFF.
line ending selector
Status bar tile
clicking the tile
when selecting a different line ending for the file
it changes the line endings in the buffer
timeout: timed out after 60000 msec waiting for something to happen
when modal is exited
it leaves the tile selection as-is
Expected 'CRLF' to be ''.
at jasmine.Spec.runs (/Users/distiller/atom/node_modules/line-ending-selector/spec/line-ending-selector-spec.js:24:50)
timeout: timed out after 60000 msec waiting for something to happen
closing the last text editor
it displays no line ending in the status bar
Expected 'CRLF' to be ''.
at jasmine.Spec.runs (/Users/distiller/atom/node_modules/line-ending-selector/spec/line-ending-selector-spec.js:24:50)
Expected '' to be 'CRLF'.
at lineEndingTile.onDidChange (/Users/distiller/atom/node_modules/line-ending-selector/spec/line-ending-selector-spec.js:232:58)
at Function.module.exports.Emitter.simpleDispatch (/Users/distiller/atom/node_modules/event-kit/lib/emitter.js:25:14)
at Emitter.module.exports.Emitter.emit (/Users/distiller/atom/node_modules/event-kit/lib/emitter.js:141:28)
at StatusBarItem.setLineEndings (/Users/distiller/atom/node_modules/line-ending-selector/lib/status-bar-item.js:15:18)
at /Users/distiller/atom/out/app/node_modules/line-ending-selector/lib/main.js:104:21
at Function.module.exports.Emitter.simpleDispatch (/Users/distiller/atom/node_modules/event-kit/lib/emitter.js:25:14)
at Emitter.module.exports.Emitter.emit (/Users/distiller/atom/node_modules/event-kit/lib/emitter.js:141:28)
at Workspace.didChangeActivePaneItemOnPaneContainer (/Users/distiller/atom/src/workspace.js:438:22)
at WorkspaceCenter.paneContainer.onDidChangeActivePaneItem (/Users/distiller/atom/src/workspace-center.js:17:14)
at Function.module.exports.Emitter.simpleDispatch (/Users/distiller/atom/node_modules/event-kit/lib/emitter.js:25:14)
at Emitter.module.exports.Emitter.emit (/Users/distiller/atom/node_modules/event-kit/lib/emitter.js:141:28)
at PaneContainer.didChangeActiveItemOnPane (/Users/distiller/atom/src/pane-container.js:281:20)
at Pane.setActiveItem (/Users/distiller/atom/src/pane.js:440:42)
at Pane.removeItem (/Users/distiller/atom/src/pane.js:694:14)
at Pane.destroyItem (/Users/distiller/atom/src/pane.js:779:10)
at Promise.all.getItems.map.item (/Users/distiller/atom/src/pane.js:787:40)
at Array.map (<anonymous>)
at Pane.destroyItems (/Users/distiller/atom/src/pane.js:787:23)
at Pane.destroy (/Users/distiller/atom/src/pane.js:1024:19)
at atom.workspace.open.then (/Users/distiller/atom/node_modules/line-ending-selector/spec/line-ending-selector-spec.js:258:44)
at <anonymous>
Finished in 121.406 seconds
14 tests, 70 assertions, 5 failures, 0 skipped
```
| 1.0 | Flaky tests: line ending selector Status bar tile ... - We've seen the line-ending-selector tests below fail twice in the past week:
https://circleci.com/gh/atom/atom/7475
https://circleci.com/gh/atom/atom/7499
Rebuilding can resolve the failures:
<img width="1065" alt="circleci" src="https://user-images.githubusercontent.com/2988/40060813-7467c768-5825-11e8-8bad-0836c878e6b5.png">
These recent failures are correlated with the recent Electron 2.0 upgrade (#17273), although we've seen these failures before (e.g., https://circleci.com/gh/atom/atom/7267).
### Failures
```
Package tests failed for line-ending-selector:
..........FFF.
line ending selector
Status bar tile
clicking the tile
when selecting a different line ending for the file
it changes the line endings in the buffer
timeout: timed out after 60000 msec waiting for something to happen
when modal is exited
it leaves the tile selection as-is
Expected 'CRLF' to be ''.
at jasmine.Spec.runs (/Users/distiller/atom/node_modules/line-ending-selector/spec/line-ending-selector-spec.js:24:50)
timeout: timed out after 60000 msec waiting for something to happen
closing the last text editor
it displays no line ending in the status bar
Expected 'CRLF' to be ''.
at jasmine.Spec.runs (/Users/distiller/atom/node_modules/line-ending-selector/spec/line-ending-selector-spec.js:24:50)
Expected '' to be 'CRLF'.
at lineEndingTile.onDidChange (/Users/distiller/atom/node_modules/line-ending-selector/spec/line-ending-selector-spec.js:232:58)
at Function.module.exports.Emitter.simpleDispatch (/Users/distiller/atom/node_modules/event-kit/lib/emitter.js:25:14)
at Emitter.module.exports.Emitter.emit (/Users/distiller/atom/node_modules/event-kit/lib/emitter.js:141:28)
at StatusBarItem.setLineEndings (/Users/distiller/atom/node_modules/line-ending-selector/lib/status-bar-item.js:15:18)
at /Users/distiller/atom/out/app/node_modules/line-ending-selector/lib/main.js:104:21
at Function.module.exports.Emitter.simpleDispatch (/Users/distiller/atom/node_modules/event-kit/lib/emitter.js:25:14)
at Emitter.module.exports.Emitter.emit (/Users/distiller/atom/node_modules/event-kit/lib/emitter.js:141:28)
at Workspace.didChangeActivePaneItemOnPaneContainer (/Users/distiller/atom/src/workspace.js:438:22)
at WorkspaceCenter.paneContainer.onDidChangeActivePaneItem (/Users/distiller/atom/src/workspace-center.js:17:14)
at Function.module.exports.Emitter.simpleDispatch (/Users/distiller/atom/node_modules/event-kit/lib/emitter.js:25:14)
at Emitter.module.exports.Emitter.emit (/Users/distiller/atom/node_modules/event-kit/lib/emitter.js:141:28)
at PaneContainer.didChangeActiveItemOnPane (/Users/distiller/atom/src/pane-container.js:281:20)
at Pane.setActiveItem (/Users/distiller/atom/src/pane.js:440:42)
at Pane.removeItem (/Users/distiller/atom/src/pane.js:694:14)
at Pane.destroyItem (/Users/distiller/atom/src/pane.js:779:10)
at Promise.all.getItems.map.item (/Users/distiller/atom/src/pane.js:787:40)
at Array.map (<anonymous>)
at Pane.destroyItems (/Users/distiller/atom/src/pane.js:787:23)
at Pane.destroy (/Users/distiller/atom/src/pane.js:1024:19)
at atom.workspace.open.then (/Users/distiller/atom/node_modules/line-ending-selector/spec/line-ending-selector-spec.js:258:44)
at <anonymous>
Finished in 121.406 seconds
14 tests, 70 assertions, 5 failures, 0 skipped
```
| non_defect | flaky tests line ending selector status bar tile we ve seen the line ending selector tests below fail twice in the past week rebuilding can resolve the failures img width alt circleci src these recent failures are correlated with the recent electron upgrade although we ve seen these failures before e g failures package tests failed for line ending selector fff line ending selector status bar tile clicking the tile when selecting a different line ending for the file it changes the line endings in the buffer timeout timed out after msec waiting for something to happen when modal is exited it leaves the tile selection as is expected crlf to be at jasmine spec runs users distiller atom node modules line ending selector spec line ending selector spec js timeout timed out after msec waiting for something to happen closing the last text editor it displays no line ending in the status bar expected crlf to be at jasmine spec runs users distiller atom node modules line ending selector spec line ending selector spec js expected to be crlf at lineendingtile ondidchange users distiller atom node modules line ending selector spec line ending selector spec js at function module exports emitter simpledispatch users distiller atom node modules event kit lib emitter js at emitter module exports emitter emit users distiller atom node modules event kit lib emitter js at statusbaritem setlineendings users distiller atom node modules line ending selector lib status bar item js at users distiller atom out app node modules line ending selector lib main js at function module exports emitter simpledispatch users distiller atom node modules event kit lib emitter js at emitter module exports emitter emit users distiller atom node modules event kit lib emitter js at workspace didchangeactivepaneitemonpanecontainer users distiller atom src workspace js at workspacecenter panecontainer ondidchangeactivepaneitem users distiller atom src workspace center js at function module exports emitter simpledispatch users distiller atom node modules event kit lib emitter js at emitter module exports emitter emit users distiller atom node modules event kit lib emitter js at panecontainer didchangeactiveitemonpane users distiller atom src pane container js at pane setactiveitem users distiller atom src pane js at pane removeitem users distiller atom src pane js at pane destroyitem users distiller atom src pane js at promise all getitems map item users distiller atom src pane js at array map at pane destroyitems users distiller atom src pane js at pane destroy users distiller atom src pane js at atom workspace open then users distiller atom node modules line ending selector spec line ending selector spec js at finished in seconds tests assertions failures skipped | 0 |
241,060 | 26,256,620,219 | IssuesEvent | 2023-01-06 01:42:17 | jinhogate/pizza_angular | https://api.github.com/repos/jinhogate/pizza_angular | opened | CVE-2022-24999 (High) detected in qs-6.5.1.tgz | security vulnerability | ## CVE-2022-24999 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>qs-6.5.1.tgz</b></p></summary>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-6.5.1.tgz">https://registry.npmjs.org/qs/-/qs-6.5.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/body-parser/node_modules/qs/package.json,/node_modules/express/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- karma-3.0.0.tgz (Root Library)
- body-parser-1.18.2.tgz
- :x: **qs-6.5.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jinhogate/pizza_angular/commit/353ead6609cbe90c767728d4050746689c22c532">353ead6609cbe90c767728d4050746689c22c532</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
qs before 6.10.3, as used in Express before 4.17.3 and other products, allows attackers to cause a Node process hang for an Express application because an __ proto__ key can be used. In many typical Express use cases, an unauthenticated remote attacker can place the attack payload in the query string of the URL that is used to visit the application, such as a[__proto__]=b&a[__proto__]&a[length]=100000000. The fix was backported to qs 6.9.7, 6.8.3, 6.7.3, 6.6.1, 6.5.3, 6.4.1, 6.3.3, and 6.2.4 (and therefore Express 4.17.3, which has "deps: qs@6.9.7" in its release description, is not vulnerable).
<p>Publish Date: 2022-11-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24999>CVE-2022-24999</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-24999">https://www.cve.org/CVERecord?id=CVE-2022-24999</a></p>
<p>Release Date: 2022-11-26</p>
<p>Fix Resolution (qs): 6.5.3</p>
<p>Direct dependency fix Resolution (karma): 3.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-24999 (High) detected in qs-6.5.1.tgz - ## CVE-2022-24999 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>qs-6.5.1.tgz</b></p></summary>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-6.5.1.tgz">https://registry.npmjs.org/qs/-/qs-6.5.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/body-parser/node_modules/qs/package.json,/node_modules/express/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- karma-3.0.0.tgz (Root Library)
- body-parser-1.18.2.tgz
- :x: **qs-6.5.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jinhogate/pizza_angular/commit/353ead6609cbe90c767728d4050746689c22c532">353ead6609cbe90c767728d4050746689c22c532</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
qs before 6.10.3, as used in Express before 4.17.3 and other products, allows attackers to cause a Node process hang for an Express application because an __ proto__ key can be used. In many typical Express use cases, an unauthenticated remote attacker can place the attack payload in the query string of the URL that is used to visit the application, such as a[__proto__]=b&a[__proto__]&a[length]=100000000. The fix was backported to qs 6.9.7, 6.8.3, 6.7.3, 6.6.1, 6.5.3, 6.4.1, 6.3.3, and 6.2.4 (and therefore Express 4.17.3, which has "deps: qs@6.9.7" in its release description, is not vulnerable).
<p>Publish Date: 2022-11-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24999>CVE-2022-24999</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-24999">https://www.cve.org/CVERecord?id=CVE-2022-24999</a></p>
<p>Release Date: 2022-11-26</p>
<p>Fix Resolution (qs): 6.5.3</p>
<p>Direct dependency fix Resolution (karma): 3.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_defect | cve high detected in qs tgz cve high severity vulnerability vulnerable library qs tgz a querystring parser that supports nesting and arrays with a depth limit library home page a href path to dependency file package json path to vulnerable library node modules body parser node modules qs package json node modules express node modules qs package json dependency hierarchy karma tgz root library body parser tgz x qs tgz vulnerable library found in head commit a href found in base branch master vulnerability details qs before as used in express before and other products allows attackers to cause a node process hang for an express application because an proto key can be used in many typical express use cases an unauthenticated remote attacker can place the attack payload in the query string of the url that is used to visit the application such as a b a a the fix was backported to qs and and therefore express which has deps qs in its release description is not vulnerable publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution qs direct dependency fix resolution karma step up your open source security game with mend | 0 |
14,139 | 2,789,931,775 | IssuesEvent | 2015-05-08 22:30:34 | google/google-visualization-api-issues | https://api.github.com/repos/google/google-visualization-api-issues | closed | ColumnChart setSelection Does Nothing | Priority-Medium Type-Defect | Original [issue 553](https://code.google.com/p/google-visualization-api-issues/issues/detail?id=553) created by orwant on 2011-03-18T17:01:11.000Z:
I am attempting to set the selection of a column chart but it never seems to allow the selection programatically.
See code sample below (taken from the Code Playground) to replicate problem.
<b>What steps will reproduce the problem? Please provide a link to a</b>
<b>demonstration page if at all possible, or attach code.</b>
// Create and populate the data table.
var data = new google.visualization.DataTable();
var raw_data = [['Austria', 1336060, 1538156, 1576579, 1600652, 1968113, 1901067],['Belgium', 3817614, 3968305, 4063225, 4604684, 4013653, 6792087],['Czech Republic', 974066, 928875, 1063414, 940478, 1037079, 1037327],['Finland', 1104797, 1151983, 1156441, 1167979, 1207029, 1284795],['France', 6651824, 5940129, 5714009, 6190532, 6420270, 6240921],['Germany', 15727003, 17356071, 16716049, 18542843, 19564053, 19830493]];
var years = [2003, 2004, 2005, 2006, 2007, 2008];
data.addColumn('string', 'Year');
for (var i = 0; i < raw_data.length; ++i) {
data.addColumn('number', raw_data[i][0]);
}
data.addRows(years.length);
for (var j = 0; j < years.length; ++j) {
data.setValue(j, 0, years[j].toString());
}
for (var i = 0; i < raw_data.length; ++i) {
for (var j = 1; j < raw_data[i].length; ++j) {
data.setValue(j-1, i+1, raw_data[i][j]);
}
}
// Create and draw the visualization.
var v = new google.visualization.ColumnChart(document.getElementById('visualization'));
v.draw(data,{title:"Yearly Coffee Consumption by Country",
width:600, height:400, hAxis: {title: "Year"}});
setTimeout(function() {
// None of these work
v.setSelection([{row:null,column:2}]);
//v.setSelection([{column:2}]);
//v.setSelection([{row:1,column:2}]);
//v.setSelection([{row:1}]);
}, 2000);
<b>What component is this issue related to (PieChart, LineChart, DataTable,</b>
<b>Query, etc)?</b>
I have been able to achieve the same with the BarChart as well.
<b>Are you using the test environment (version 1.1)?</b>
<b>(If you are not sure, answer NO)</b>
No
<b>What operating system and browser are you using?</b>
Windows 7 64bit, Chrome v10.0.648.127
<b>*********************************************************</b>
<b>For developers viewing this issue: please click the 'star' icon to be</b>
<b>notified of future changes, and to let us know how many of you are</b>
<b>interested in seeing it resolved.</b>
<b>*********************************************************</b>
| 1.0 | ColumnChart setSelection Does Nothing - Original [issue 553](https://code.google.com/p/google-visualization-api-issues/issues/detail?id=553) created by orwant on 2011-03-18T17:01:11.000Z:
I am attempting to set the selection of a column chart but it never seems to allow the selection programatically.
See code sample below (taken from the Code Playground) to replicate problem.
<b>What steps will reproduce the problem? Please provide a link to a</b>
<b>demonstration page if at all possible, or attach code.</b>
// Create and populate the data table.
var data = new google.visualization.DataTable();
var raw_data = [['Austria', 1336060, 1538156, 1576579, 1600652, 1968113, 1901067],['Belgium', 3817614, 3968305, 4063225, 4604684, 4013653, 6792087],['Czech Republic', 974066, 928875, 1063414, 940478, 1037079, 1037327],['Finland', 1104797, 1151983, 1156441, 1167979, 1207029, 1284795],['France', 6651824, 5940129, 5714009, 6190532, 6420270, 6240921],['Germany', 15727003, 17356071, 16716049, 18542843, 19564053, 19830493]];
var years = [2003, 2004, 2005, 2006, 2007, 2008];
data.addColumn('string', 'Year');
for (var i = 0; i < raw_data.length; ++i) {
data.addColumn('number', raw_data[i][0]);
}
data.addRows(years.length);
for (var j = 0; j < years.length; ++j) {
data.setValue(j, 0, years[j].toString());
}
for (var i = 0; i < raw_data.length; ++i) {
for (var j = 1; j < raw_data[i].length; ++j) {
data.setValue(j-1, i+1, raw_data[i][j]);
}
}
// Create and draw the visualization.
var v = new google.visualization.ColumnChart(document.getElementById('visualization'));
v.draw(data,{title:"Yearly Coffee Consumption by Country",
width:600, height:400, hAxis: {title: "Year"}});
setTimeout(function() {
// None of these work
v.setSelection([{row:null,column:2}]);
//v.setSelection([{column:2}]);
//v.setSelection([{row:1,column:2}]);
//v.setSelection([{row:1}]);
}, 2000);
<b>What component is this issue related to (PieChart, LineChart, DataTable,</b>
<b>Query, etc)?</b>
I have been able to achieve the same with the BarChart as well.
<b>Are you using the test environment (version 1.1)?</b>
<b>(If you are not sure, answer NO)</b>
No
<b>What operating system and browser are you using?</b>
Windows 7 64bit, Chrome v10.0.648.127
<b>*********************************************************</b>
<b>For developers viewing this issue: please click the 'star' icon to be</b>
<b>notified of future changes, and to let us know how many of you are</b>
<b>interested in seeing it resolved.</b>
<b>*********************************************************</b>
| defect | columnchart setselection does nothing original created by orwant on i am attempting to set the selection of a column chart but it never seems to allow the selection programatically see code sample below taken from the code playground to replicate problem what steps will reproduce the problem please provide a link to a demonstration page if at all possible or attach code create and populate the data table var data new google visualization datatable var raw data var years data addcolumn string year for var i i lt raw data length i data addcolumn number raw data data addrows years length for var j j lt years length j data setvalue j years tostring for var i i lt raw data length i for var j j lt raw data length j data setvalue j i raw data create and draw the visualization var v new google visualization columnchart document getelementbyid visualization v draw data title quot yearly coffee consumption by country quot width height haxis title quot year quot settimeout function none of these work v setselection v setselection v setselection v setselection what component is this issue related to piechart linechart datatable query etc i have been able to achieve the same with the barchart as well are you using the test environment version if you are not sure answer no no what operating system and browser are you using windows chrome for developers viewing this issue please click the star icon to be notified of future changes and to let us know how many of you are interested in seeing it resolved | 1 |
65,094 | 19,094,887,220 | IssuesEvent | 2021-11-29 15:43:53 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | closed | [Assistive tech and device support] Pages require sensory characteristics to be understood or operable. (11.11.1) | content 508/Accessibility 508-defect-1 vsa-search-discovery collab-cycle-feedback Staging launch-blocking CCIssue11.11 CC-Dashboard | ### General Information
#### VFS team name
Search & Discovery
#### VFS product name
Typeahead 2.0
#### Point of Contact/Reviewers
Josh Kim (Accessibility) @joshkimux
---
### Platform Issue
Pages require sensory characteristics to be understood or operable.
### Issue Details
Announcements to screen reader users that options are available and instructions on how to interact with suggestions are not available.
### Link, screenshot or steps to recreate
1. Using your choice of screen reader, type "10-10" into the staging search box. Confirm that there is no announcement.
2. Repeat on va.gov. Confirm there is an announcement, but no additional instructions on search to enter.
### VA.gov Experience Standard
[Category Number 11, Issue Number 11](https://depo-platform-documentation.scrollhelp.site/collaboration-cycle/VA.gov-experience-standards.1683980311.html)
### Other References
WCAG SC 1.3.3_A
---
### Platform Recommendation
We recommend referencing gov.uk's usage of `aria-describedby` to provide additional "hints" on how to navigate and use the suggestions list (specifically, arrow keys and using enter to search). This should be separate from the announcement on how many suggestions exist when they expand out (x of x results).
### VFS Team Tasks to Complete
- [ ] Comment on the ticket if there are questions or concerns
- [ ] VFS team closes the ticket when the issue has been resolved | 1.0 | [Assistive tech and device support] Pages require sensory characteristics to be understood or operable. (11.11.1) - ### General Information
#### VFS team name
Search & Discovery
#### VFS product name
Typeahead 2.0
#### Point of Contact/Reviewers
Josh Kim (Accessibility) @joshkimux
---
### Platform Issue
Pages require sensory characteristics to be understood or operable.
### Issue Details
Announcements to screen reader users that options are available and instructions on how to interact with suggestions are not available.
### Link, screenshot or steps to recreate
1. Using your choice of screen reader, type "10-10" into the staging search box. Confirm that there is no announcement.
2. Repeat on va.gov. Confirm there is an announcement, but no additional instructions on search to enter.
### VA.gov Experience Standard
[Category Number 11, Issue Number 11](https://depo-platform-documentation.scrollhelp.site/collaboration-cycle/VA.gov-experience-standards.1683980311.html)
### Other References
WCAG SC 1.3.3_A
---
### Platform Recommendation
We recommend referencing gov.uk's usage of `aria-describedby` to provide additional "hints" on how to navigate and use the suggestions list (specifically, arrow keys and using enter to search). This should be separate from the announcement on how many suggestions exist when they expand out (x of x results).
### VFS Team Tasks to Complete
- [ ] Comment on the ticket if there are questions or concerns
- [ ] VFS team closes the ticket when the issue has been resolved | defect | pages require sensory characteristics to be understood or operable general information vfs team name search discovery vfs product name typeahead point of contact reviewers josh kim accessibility joshkimux platform issue pages require sensory characteristics to be understood or operable issue details announcements to screen reader users that options are available and instructions on how to interact with suggestions are not available link screenshot or steps to recreate using your choice of screen reader type into the staging search box confirm that there is no announcement repeat on va gov confirm there is an announcement but no additional instructions on search to enter va gov experience standard other references wcag sc a platform recommendation we recommend referencing gov uk s usage of aria describedby to provide additional hints on how to navigate and use the suggestions list specifically arrow keys and using enter to search this should be separate from the announcement on how many suggestions exist when they expand out x of x results vfs team tasks to complete comment on the ticket if there are questions or concerns vfs team closes the ticket when the issue has been resolved | 1 |
16,594 | 2,919,871,755 | IssuesEvent | 2015-06-24 16:08:14 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | closed | MaxSizeChecker.getApproximateMaxSize: implicit cast to int breaks isEvictableHeapPercentage, possibly others | Team: Core Type: Defect | When the eviction policy of a distributed IMap is set to heap percentage with a threshold of 1%, MaxSizeChecker will invoke isEvictableHeapPercentage when determining whether to evict entries. getApproximateMaxSize will then be invoked with a maxSizeFromConfig argument of 1.
Because the return type of getApproximateMaxSize is an int, the expression:
`maxSizeFromConfig * EVICTION_START_THRESHOLD_PERCENTAGE / ONE_HUNDRED_PERCENT `
will be cast from 0.95 to 0, such that:
`maxSize < (1D * ONE_HUNDRED_PERCENT * usedHeapSize / total)`
will always evaluate to true, and entries will always be evicted. | 1.0 | MaxSizeChecker.getApproximateMaxSize: implicit cast to int breaks isEvictableHeapPercentage, possibly others - When the eviction policy of a distributed IMap is set to heap percentage with a threshold of 1%, MaxSizeChecker will invoke isEvictableHeapPercentage when determining whether to evict entries. getApproximateMaxSize will then be invoked with a maxSizeFromConfig argument of 1.
Because the return type of getApproximateMaxSize is an int, the expression:
`maxSizeFromConfig * EVICTION_START_THRESHOLD_PERCENTAGE / ONE_HUNDRED_PERCENT `
will be cast from 0.95 to 0, such that:
`maxSize < (1D * ONE_HUNDRED_PERCENT * usedHeapSize / total)`
will always evaluate to true, and entries will always be evicted. | defect | maxsizechecker getapproximatemaxsize implicit cast to int breaks isevictableheappercentage possibly others when the eviction policy of a distributed imap is set to heap percentage with a threshold of maxsizechecker will invoke isevictableheappercentage when determining whether to evict entries getapproximatemaxsize will then be invoked with a maxsizefromconfig argument of because the return type of getapproximatemaxsize is an int the expression maxsizefromconfig eviction start threshold percentage one hundred percent will be cast from to such that maxsize one hundred percent usedheapsize total will always evaluate to true and entries will always be evicted | 1 |
81,606 | 23,510,520,820 | IssuesEvent | 2022-08-18 16:05:31 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | opened | `zathura` fails to build | 0.kind: build failure | ### Steps To Reproduce
`build .#zathura` on Nixpkgs unstable small, commit hash `6e665c4e29613872fb48c4b645aed0c28fb93702` (`x86 linux`).
### Build log
```
[zathura.log](https://github.com/NixOS/nixpkgs/files/9375515/zathura.log)```
### Additional context
There is an upstream bug report, but it has not been addressed yet: https://git.pwmt.org/pwmt/zathura-pdf-mupdf/-/issues/29.
### Notify maintainers
@cstrahan
| 1.0 | `zathura` fails to build - ### Steps To Reproduce
`build .#zathura` on Nixpkgs unstable small, commit hash `6e665c4e29613872fb48c4b645aed0c28fb93702` (`x86 linux`).
### Build log
```
[zathura.log](https://github.com/NixOS/nixpkgs/files/9375515/zathura.log)```
### Additional context
There is an upstream bug report, but it has not been addressed yet: https://git.pwmt.org/pwmt/zathura-pdf-mupdf/-/issues/29.
### Notify maintainers
@cstrahan
| non_defect | zathura fails to build steps to reproduce build zathura on nixpkgs unstable small commit hash linux build log additional context there is an upstream bug report but it has not been addressed yet notify maintainers cstrahan | 0 |
215,673 | 7,296,573,272 | IssuesEvent | 2018-02-26 11:14:12 | wso2/product-is | https://api.github.com/repos/wso2/product-is | opened | No tooltips for any of the buttons in the Dashboard | Affected/5.5.0-Alpha2 Priority/High Severity/Minor Type/Improvement | The following were noted in the Consent Management UI
| 1.0 | No tooltips for any of the buttons in the Dashboard - The following were noted in the Consent Management UI
| non_defect | no tooltips for any of the buttons in the dashboard the following were noted in the consent management ui | 0 |
9,889 | 3,975,922,257 | IssuesEvent | 2016-05-05 08:51:01 | oppia/oppia | https://api.github.com/repos/oppia/oppia | closed | Save/publish button and the caret button do not have the same height | bug: minor frontend/editor-main starter project TODO: code | Here is what the save/publish button looks like in the editor on narrower screens (see the right side of the following screenshot):

This looks messy, and it would be better if the button and the "caret button" next to it had the same height. | 1.0 | Save/publish button and the caret button do not have the same height - Here is what the save/publish button looks like in the editor on narrower screens (see the right side of the following screenshot):

This looks messy, and it would be better if the button and the "caret button" next to it had the same height. | non_defect | save publish button and the caret button do not have the same height here is what the save publish button looks like in the editor on narrower screens see the right side of the following screenshot this looks messy and it would be better if the button and the caret button next to it had the same height | 0 |
9,519 | 8,656,537,282 | IssuesEvent | 2018-11-27 18:44:36 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Need clarity on => Permissions to create a service principal with the Contributor role on your Azure subscription? | awaiting-product-team-response container-service/svc cxp in-progress product-question triaged | Can you explain this statement? In the above article is create-for-rbac is expected to have contributor role on the subscription? if so why? should it have any specific permissions? What if I already have a service account and don't want to create it as part of this process wherein I am scripting out all of the steps?
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 77905ec1-fd7e-d037-cac5-62a5b8075c1b
* Version Independent ID: 239518e8-cb47-3fd3-9cc2-2238ef57cbc6
* Content: [Integrate with Azure-managed services using Open Service Broker for Azure (OSBA)](https://docs.microsoft.com/en-us/azure/aks/integrate-azure)
* Content Source: [articles/aks/integrate-azure.md](https://github.com/Microsoft/azure-docs/blob/master/articles/aks/integrate-azure.md)
* Service: **container-service**
* GitHub Login: @sozercan
* Microsoft Alias: **seozerca** | 1.0 | Need clarity on => Permissions to create a service principal with the Contributor role on your Azure subscription? - Can you explain this statement? In the above article is create-for-rbac is expected to have contributor role on the subscription? if so why? should it have any specific permissions? What if I already have a service account and don't want to create it as part of this process wherein I am scripting out all of the steps?
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 77905ec1-fd7e-d037-cac5-62a5b8075c1b
* Version Independent ID: 239518e8-cb47-3fd3-9cc2-2238ef57cbc6
* Content: [Integrate with Azure-managed services using Open Service Broker for Azure (OSBA)](https://docs.microsoft.com/en-us/azure/aks/integrate-azure)
* Content Source: [articles/aks/integrate-azure.md](https://github.com/Microsoft/azure-docs/blob/master/articles/aks/integrate-azure.md)
* Service: **container-service**
* GitHub Login: @sozercan
* Microsoft Alias: **seozerca** | non_defect | need clarity on permissions to create a service principal with the contributor role on your azure subscription can you explain this statement in the above article is create for rbac is expected to have contributor role on the subscription if so why should it have any specific permissions what if i already have a service account and don t want to create it as part of this process wherein i am scripting out all of the steps document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service container service github login sozercan microsoft alias seozerca | 0 |
178,204 | 13,768,558,183 | IssuesEvent | 2020-10-07 17:15:55 | flutter/flutter | https://api.github.com/repos/flutter/flutter | closed | Test `testSetFlutterViewControllerAfterCreateCanStillDispatchTouchEvents` on engine iOS tests is flaky | P3 a: platform-views a: tests passed first triage team: flakes | The test is flaky.
Log:
https://logs.chromium.org/logs/flutter/buildbucket/cr-buildbucket.appspot.com/8870773991329664432/+/steps/Host_Tests_for_ios_debug_sim/0/stdout?format=raw | 1.0 | Test `testSetFlutterViewControllerAfterCreateCanStillDispatchTouchEvents` on engine iOS tests is flaky - The test is flaky.
Log:
https://logs.chromium.org/logs/flutter/buildbucket/cr-buildbucket.appspot.com/8870773991329664432/+/steps/Host_Tests_for_ios_debug_sim/0/stdout?format=raw | non_defect | test testsetflutterviewcontrolleraftercreatecanstilldispatchtouchevents on engine ios tests is flaky the test is flaky log | 0 |
21,597 | 3,521,808,726 | IssuesEvent | 2016-01-13 05:02:00 | toopriddy/mytime | https://api.github.com/repos/toopriddy/mytime | closed | Duplicate hour category for construction | auto-migrated Priority-Medium Type-Defect | ```
!!! PLEASE ANSWER THE 9 QUESTIONS HERE: !!!
Please fill out ALL of this form (there are several questions in this text
entry
box you need to answer, you will have to scroll down to answer them)
This is for BUGS only, feature requests are done at
http://code.google.com/p/mytime/wiki/Wishlist or email me
NEVER POST PERSONAL INFORMATION IN A BUG REPORT!
================================================
1. What steps will reproduce the problem? (please include step by step
detail
like you were going to explain how to do this to someone who has never seen
this program before and has a hard time following your instructions, things
obvious to you might not be obvious when trying to reproduce the issues) I
have left you space below to include your 10-20 steps to reproduce the
problem:
I added a new hour category which allowed me to record extra hour for some
Bethel work. Afterwards the hour category “Construction” was duplicated and
cannot be deleted. I have automatically twice the category “Construction”
(I have the German localization and I’m not sure about the English names).
================================================
2. What is the expected output? What do you see instead? (Please attach a
screenshot or
email one; capture a screenshot by pressing on the power and home buttons
at the same time.
The resulting screenshot will be in the Photos application in the "Camera
Roll")
See Attachements
================================================
3. Is this running on an iPhone, iPhone 3G or iTouch?
iPhone 5
================================================
4. What version of the iPhone/iTouch are you using (from the home screen go to
Settings->General->About->Version) it will be something like 2.1, 2.2, 2.2.1?
6.0.2
================================================
5. What version of MyTime are you running? (look for this in
MyTime->More->Settings->MyTime Version)
Newest
================================================
6. What language do you have your iPhone set to?
German
================================================
7. Please provide any additional information below that you feel would help me
to reproduce this problem
-
================================================
8. Your issue might need some help reproducing; start the Settings app on
the home screen then scroll down to "MyTime" and press on it, now turn on the
"Email Backup Instantly"
switch, now quit the Settings application and start MyTime and send the
email to
toopriddy@gmail.com
I always delete the data after the bug has been reproduced and fixed.
================================================
9. If you are reporting a crash, please follow the instructions at
http://code.google.com/p/mytime/wiki/CrashReport to send me your crash
reports
```
Original issue reported on code.google.com by `niva...@gmx.net` on 27 Dec 2012 at 3:47
Attachments:
* [Foto 1.PNG](https://storage.googleapis.com/google-code-attachments/mytime/issue-214/comment-0/Foto 1.PNG)
* [Foto 2.PNG](https://storage.googleapis.com/google-code-attachments/mytime/issue-214/comment-0/Foto 2.PNG)
* [Foto 3.PNG](https://storage.googleapis.com/google-code-attachments/mytime/issue-214/comment-0/Foto 3.PNG)
* [Foto 4.PNG](https://storage.googleapis.com/google-code-attachments/mytime/issue-214/comment-0/Foto 4.PNG)
| 1.0 | Duplicate hour category for construction - ```
!!! PLEASE ANSWER THE 9 QUESTIONS HERE: !!!
Please fill out ALL of this form (there are several questions in this text
entry
box you need to answer, you will have to scroll down to answer them)
This is for BUGS only, feature requests are done at
http://code.google.com/p/mytime/wiki/Wishlist or email me
NEVER POST PERSONAL INFORMATION IN A BUG REPORT!
================================================
1. What steps will reproduce the problem? (please include step by step
detail
like you were going to explain how to do this to someone who has never seen
this program before and has a hard time following your instructions, things
obvious to you might not be obvious when trying to reproduce the issues) I
have left you space below to include your 10-20 steps to reproduce the
problem:
I added a new hour category which allowed me to record extra hour for some
Bethel work. Afterwards the hour category “Construction” was duplicated and
cannot be deleted. I have automatically twice the category “Construction”
(I have the German localization and I’m not sure about the English names).
================================================
2. What is the expected output? What do you see instead? (Please attach a
screenshot or
email one; capture a screenshot by pressing on the power and home buttons
at the same time.
The resulting screenshot will be in the Photos application in the "Camera
Roll")
See Attachements
================================================
3. Is this running on an iPhone, iPhone 3G or iTouch?
iPhone 5
================================================
4. What version of the iPhone/iTouch are you using (from the home screen go to
Settings->General->About->Version) it will be something like 2.1, 2.2, 2.2.1?
6.0.2
================================================
5. What version of MyTime are you running? (look for this in
MyTime->More->Settings->MyTime Version)
Newest
================================================
6. What language do you have your iPhone set to?
German
================================================
7. Please provide any additional information below that you feel would help me
to reproduce this problem
-
================================================
8. Your issue might need some help reproducing; start the Settings app on
the home screen then scroll down to "MyTime" and press on it, now turn on the
"Email Backup Instantly"
switch, now quit the Settings application and start MyTime and send the
email to
toopriddy@gmail.com
I always delete the data after the bug has been reproduced and fixed.
================================================
9. If you are reporting a crash, please follow the instructions at
http://code.google.com/p/mytime/wiki/CrashReport to send me your crash
reports
```
Original issue reported on code.google.com by `niva...@gmx.net` on 27 Dec 2012 at 3:47
Attachments:
* [Foto 1.PNG](https://storage.googleapis.com/google-code-attachments/mytime/issue-214/comment-0/Foto 1.PNG)
* [Foto 2.PNG](https://storage.googleapis.com/google-code-attachments/mytime/issue-214/comment-0/Foto 2.PNG)
* [Foto 3.PNG](https://storage.googleapis.com/google-code-attachments/mytime/issue-214/comment-0/Foto 3.PNG)
* [Foto 4.PNG](https://storage.googleapis.com/google-code-attachments/mytime/issue-214/comment-0/Foto 4.PNG)
| defect | duplicate hour category for construction please answer the questions here please fill out all of this form there are several questions in this text entry box you need to answer you will have to scroll down to answer them this is for bugs only feature requests are done at or email me never post personal information in a bug report what steps will reproduce the problem please include step by step detail like you were going to explain how to do this to someone who has never seen this program before and has a hard time following your instructions things obvious to you might not be obvious when trying to reproduce the issues i have left you space below to include your steps to reproduce the problem i added a new hour category which allowed me to record extra hour for some bethel work afterwards the hour category “construction” was duplicated and cannot be deleted i have automatically twice the category “construction” i have the german localization and i’m not sure about the english names what is the expected output what do you see instead please attach a screenshot or email one capture a screenshot by pressing on the power and home buttons at the same time the resulting screenshot will be in the photos application in the camera roll see attachements is this running on an iphone iphone or itouch iphone what version of the iphone itouch are you using from the home screen go to settings general about version it will be something like what version of mytime are you running look for this in mytime more settings mytime version newest what language do you have your iphone set to german please provide any additional information below that you feel would help me to reproduce this problem your issue might need some help reproducing start the settings app on the home screen then scroll down to mytime and press on it now turn on the email backup instantly switch now quit the settings application and start mytime and send the email to toopriddy gmail com i always delete the data after the bug has been reproduced and fixed if you are reporting a crash please follow the instructions at to send me your crash reports original issue reported on code google com by niva gmx net on dec at attachments png png png png | 1 |
102,200 | 31,858,057,439 | IssuesEvent | 2023-09-15 08:54:58 | moby/buildkit | https://api.github.com/repos/moby/buildkit | closed | Consider migrating from Alpine to Debian, Ubuntu, or Wolfi for reproducible builds | area/reproducible-builds | Reproducible builds is hard with Alpine, as Alpine does not keep old packages: https://gitlab.alpinelinux.org/alpine/abuild/-/issues/9996
Debian, Ubuntu, and Wolfi are more suitable for reproducible builds, as they keep old packages:
- https://snapshot-cloudflare.debian.org/
- http://snapshot.ubuntu.com/ubuntu/20230904T000000Z/dists/jammy/Release
- https://www.chainguard.dev/unchained/reproducing-chainguards-reproducible-image-builds
Wolfi currently does not support armv7, s390x, ppc64le, and riscv64 though:
- https://github.com/wolfi-dev/os/issues/5440
| 1.0 | Consider migrating from Alpine to Debian, Ubuntu, or Wolfi for reproducible builds - Reproducible builds is hard with Alpine, as Alpine does not keep old packages: https://gitlab.alpinelinux.org/alpine/abuild/-/issues/9996
Debian, Ubuntu, and Wolfi are more suitable for reproducible builds, as they keep old packages:
- https://snapshot-cloudflare.debian.org/
- http://snapshot.ubuntu.com/ubuntu/20230904T000000Z/dists/jammy/Release
- https://www.chainguard.dev/unchained/reproducing-chainguards-reproducible-image-builds
Wolfi currently does not support armv7, s390x, ppc64le, and riscv64 though:
- https://github.com/wolfi-dev/os/issues/5440
| non_defect | consider migrating from alpine to debian ubuntu or wolfi for reproducible builds reproducible builds is hard with alpine as alpine does not keep old packages debian ubuntu and wolfi are more suitable for reproducible builds as they keep old packages wolfi currently does not support and though | 0 |
78,356 | 22,203,557,047 | IssuesEvent | 2022-06-07 13:15:40 | xamarin/xamarin-android | https://api.github.com/repos/xamarin/xamarin-android | closed | Deployment to physical Android device stucks when "Fast Assembly Deployment" is active (VS Mac) | Area: App+Library Build need-attention | ### Steps to Reproduce
1. Create a new Xamarin Forms solution (iOS and Android)
2. Open the Android project options and enable the option "Fast Assembly Deployment", for the build configuration "Debug", click ok.
3. At this point there i recognize the first bug: Reopen now the Android project options again and you will see that the option "Fast Assembly Deployment" is disabled again. But this is only a visual selection bug. In the android.csproj file the property <EmbedAssembliesIntoApk> is deleted, which is ok. EmbedAssembliesIntoApk == missing: Fast Assembly Deployment = ON. EmbedAssembliesIntoApk == true: Fast Assembly Deployment = OFF
4. Lets go ahead with the real issue.
5. Now select your connected real android device. In my case its a Google Pixel 2 XL (API 30)
6. The deployprocess is running but stops in the middle of task: Fast Deploy Application Files
7. Now you can wait hours and nothing happens.
8. When you stop the deployment now and start it again, VS is broken and will not build the project again. It just stucks on building without any error. You have to restart whole VS to be able to build again
Example project zip:
[TestApp.zip](https://github.com/xamarin/xamarin-android/files/6508389/TestApp.zip)
### Expected Behavior
Should deploy to the device.
### Actual Behavior
Stucks on deployment process.
### Version Information
<!--
1. On macOS and within Visual Studio, select Visual Studio > About Visual Studio, then click the Show Details button, then click the Copy Information button.
2. Paste below this comment block.
-->
=== Visual Studio Community 2019 for Mac ===
Version 8.9.10 (build 4)
Installation UUID: 82933c53-a51e-40ef-b605-f2b4a07711f0
GTK+ 2.24.23 (Raleigh theme)
Xamarin.Mac 6.18.0.23 (d16-6 / 088c73638)
Package version: 612000125
=== Mono Framework MDK ===
Runtime:
Mono 6.12.0.125 (2020-02/8c552e98bd6) (64-bit)
Package version: 612000125
=== Roslyn (Language Service) ===
3.9.0-6.21152.10+c10f884b30737542ddd84ca889a4aad9281ce210
=== NuGet ===
Version: 5.8.0.6860
=== .NET Core SDK ===
SDK: /usr/local/share/dotnet/sdk/5.0.203/Sdks
SDK Versions:
5.0.203
5.0.202
5.0.201
5.0.103
5.0.102
3.1.409
3.1.408
3.1.407
3.1.406
3.1.402
3.1.401
3.1.302
3.1.301
3.1.300
MSBuild SDKs: /Applications/Visual Studio.app/Contents/Resources/lib/monodevelop/bin/MSBuild/Current/bin/Sdks
=== .NET Core Runtime ===
Runtime: /usr/local/share/dotnet/dotnet
Runtime Versions:
5.0.6
5.0.5
5.0.4
5.0.3
5.0.2
3.1.15
3.1.14
3.1.13
3.1.12
3.1.8
3.1.7
3.1.6
3.1.5
3.1.4
2.1.23
2.1.22
2.1.21
2.1.20
2.1.19
2.1.18
=== .NET Core 3.1 SDK ===
SDK: 3.1.409
=== Xamarin.Profiler ===
Version: 1.6.15.68
Location: /Applications/Xamarin Profiler.app/Contents/MacOS/Xamarin Profiler
=== Updater ===
Version: 11
=== Apple Developer Tools ===
Xcode 12.5 (18205)
Build 12E262
=== Xamarin.Mac ===
Xamarin.Mac not installed. Can't find /Library/Frameworks/Xamarin.Mac.framework/Versions/Current/Version.
=== Xamarin.iOS ===
Version: 14.16.0.5 (Visual Studio Community)
Hash: ab40b131d
Branch: xcode12.5
Build date: 2021-04-22 08:56:42-0400
=== Xamarin Designer ===
Version: 16.9.0.324
Hash: b1e216c75
Branch: remotes/origin/d16-9
Build date: 2021-04-16 00:02:50 UTC
=== Xamarin.Android ===
Version: 11.2.2.1 (Visual Studio Community)
Commit: xamarin-android/d16-9/877f572
Android SDK: /Users/stefan/Library/Developer/Xamarin/android-sdk-macosx
Supported Android versions:
None installed
SDK Tools Version: 26.1.1
SDK Platform Tools Version: 30.0.4
SDK Build Tools Version: 30.0.2
Build Information:
Mono: 5e9cb6d
Java.Interop: xamarin/java.interop/d16-9@54f8c24
ProGuard: Guardsquare/proguard/v7.0.1@912d149
SQLite: xamarin/sqlite/3.34.1@daff8f4
Xamarin.Android Tools: xamarin/xamarin-android-tools/d16-9@d210f11
=== Microsoft OpenJDK for Mobile ===
Java SDK: /Users/stefan/Library/Developer/Xamarin/jdk/microsoft_dist_openjdk_1.8.0.25
1.8.0-25
Android Designer EPL code available here:
https://github.com/xamarin/AndroidDesigner.EPL
=== Android SDK Manager ===
Version: 16.9.0.22
Hash: a391de2
Branch: remotes/origin/dev/bretjohn/readme-tweak~3
Build date: 2021-05-13 17:03:56 UTC
=== Android Device Manager ===
Version: 16.9.0.17
Hash: fc2b3db
Branch: remotes/origin/dev/jmt/d16-9bump~1
Build date: 2021-05-13 17:04:12 UTC
=== Build Information ===
Release ID: 809100004
Git revision: 30612572b7defb0273729cb6b5ea5adc8bd9a147
Build date: 2021-05-13 13:06:24-04
Build branch: release-8.9
Xamarin extensions: 30612572b7defb0273729cb6b5ea5adc8bd9a147
=== Operating System ===
Mac OS X 10.16.0
Darwin 20.4.0 Darwin Kernel Version 20.4.0
Fri Mar 5 01:14:14 PST 2021
root:xnu-7195.101.1~3/RELEASE_X86_64 x86_64
=== Enabled user installed extensions ===
NuGet Package Management Extensions 0.26
NuGet Package Explorer 0.6
### Log File
<!--
1. Within Visual Studio:
a. Click **Tools** > **SDK Command Prompt** on macOS or
**Tools** > **Android** > **Android Adb Command Prompt** on Windows
b. On macOS, in the launched `Terminal.app` window, run:
adb logcat -d | pbcopy
On Windows, in the launched `cmd.exe` window, run:
adb logcat -d | clip
2. Paste below this comment block
-->
[Archiv.zip](https://github.com/xamarin/xamarin-android/files/6508444/Archiv.zip)
I'v added all my log files from %Home%/Library/Logs/VisualStudio/8.0
1. I removed all logs
2. Started VS
3. Open solution
4. Rebuild the Android project
5. Deploy to real device
6. Stuck
<!--
Switch to the "Preview" tab to ensure your issue renders correctly.
-->
| 1.0 | Deployment to physical Android device stucks when "Fast Assembly Deployment" is active (VS Mac) - ### Steps to Reproduce
1. Create a new Xamarin Forms solution (iOS and Android)
2. Open the Android project options and enable the option "Fast Assembly Deployment", for the build configuration "Debug", click ok.
3. At this point there i recognize the first bug: Reopen now the Android project options again and you will see that the option "Fast Assembly Deployment" is disabled again. But this is only a visual selection bug. In the android.csproj file the property <EmbedAssembliesIntoApk> is deleted, which is ok. EmbedAssembliesIntoApk == missing: Fast Assembly Deployment = ON. EmbedAssembliesIntoApk == true: Fast Assembly Deployment = OFF
4. Lets go ahead with the real issue.
5. Now select your connected real android device. In my case its a Google Pixel 2 XL (API 30)
6. The deployprocess is running but stops in the middle of task: Fast Deploy Application Files
7. Now you can wait hours and nothing happens.
8. When you stop the deployment now and start it again, VS is broken and will not build the project again. It just stucks on building without any error. You have to restart whole VS to be able to build again
Example project zip:
[TestApp.zip](https://github.com/xamarin/xamarin-android/files/6508389/TestApp.zip)
### Expected Behavior
Should deploy to the device.
### Actual Behavior
Stucks on deployment process.
### Version Information
<!--
1. On macOS and within Visual Studio, select Visual Studio > About Visual Studio, then click the Show Details button, then click the Copy Information button.
2. Paste below this comment block.
-->
=== Visual Studio Community 2019 for Mac ===
Version 8.9.10 (build 4)
Installation UUID: 82933c53-a51e-40ef-b605-f2b4a07711f0
GTK+ 2.24.23 (Raleigh theme)
Xamarin.Mac 6.18.0.23 (d16-6 / 088c73638)
Package version: 612000125
=== Mono Framework MDK ===
Runtime:
Mono 6.12.0.125 (2020-02/8c552e98bd6) (64-bit)
Package version: 612000125
=== Roslyn (Language Service) ===
3.9.0-6.21152.10+c10f884b30737542ddd84ca889a4aad9281ce210
=== NuGet ===
Version: 5.8.0.6860
=== .NET Core SDK ===
SDK: /usr/local/share/dotnet/sdk/5.0.203/Sdks
SDK Versions:
5.0.203
5.0.202
5.0.201
5.0.103
5.0.102
3.1.409
3.1.408
3.1.407
3.1.406
3.1.402
3.1.401
3.1.302
3.1.301
3.1.300
MSBuild SDKs: /Applications/Visual Studio.app/Contents/Resources/lib/monodevelop/bin/MSBuild/Current/bin/Sdks
=== .NET Core Runtime ===
Runtime: /usr/local/share/dotnet/dotnet
Runtime Versions:
5.0.6
5.0.5
5.0.4
5.0.3
5.0.2
3.1.15
3.1.14
3.1.13
3.1.12
3.1.8
3.1.7
3.1.6
3.1.5
3.1.4
2.1.23
2.1.22
2.1.21
2.1.20
2.1.19
2.1.18
=== .NET Core 3.1 SDK ===
SDK: 3.1.409
=== Xamarin.Profiler ===
Version: 1.6.15.68
Location: /Applications/Xamarin Profiler.app/Contents/MacOS/Xamarin Profiler
=== Updater ===
Version: 11
=== Apple Developer Tools ===
Xcode 12.5 (18205)
Build 12E262
=== Xamarin.Mac ===
Xamarin.Mac not installed. Can't find /Library/Frameworks/Xamarin.Mac.framework/Versions/Current/Version.
=== Xamarin.iOS ===
Version: 14.16.0.5 (Visual Studio Community)
Hash: ab40b131d
Branch: xcode12.5
Build date: 2021-04-22 08:56:42-0400
=== Xamarin Designer ===
Version: 16.9.0.324
Hash: b1e216c75
Branch: remotes/origin/d16-9
Build date: 2021-04-16 00:02:50 UTC
=== Xamarin.Android ===
Version: 11.2.2.1 (Visual Studio Community)
Commit: xamarin-android/d16-9/877f572
Android SDK: /Users/stefan/Library/Developer/Xamarin/android-sdk-macosx
Supported Android versions:
None installed
SDK Tools Version: 26.1.1
SDK Platform Tools Version: 30.0.4
SDK Build Tools Version: 30.0.2
Build Information:
Mono: 5e9cb6d
Java.Interop: xamarin/java.interop/d16-9@54f8c24
ProGuard: Guardsquare/proguard/v7.0.1@912d149
SQLite: xamarin/sqlite/3.34.1@daff8f4
Xamarin.Android Tools: xamarin/xamarin-android-tools/d16-9@d210f11
=== Microsoft OpenJDK for Mobile ===
Java SDK: /Users/stefan/Library/Developer/Xamarin/jdk/microsoft_dist_openjdk_1.8.0.25
1.8.0-25
Android Designer EPL code available here:
https://github.com/xamarin/AndroidDesigner.EPL
=== Android SDK Manager ===
Version: 16.9.0.22
Hash: a391de2
Branch: remotes/origin/dev/bretjohn/readme-tweak~3
Build date: 2021-05-13 17:03:56 UTC
=== Android Device Manager ===
Version: 16.9.0.17
Hash: fc2b3db
Branch: remotes/origin/dev/jmt/d16-9bump~1
Build date: 2021-05-13 17:04:12 UTC
=== Build Information ===
Release ID: 809100004
Git revision: 30612572b7defb0273729cb6b5ea5adc8bd9a147
Build date: 2021-05-13 13:06:24-04
Build branch: release-8.9
Xamarin extensions: 30612572b7defb0273729cb6b5ea5adc8bd9a147
=== Operating System ===
Mac OS X 10.16.0
Darwin 20.4.0 Darwin Kernel Version 20.4.0
Fri Mar 5 01:14:14 PST 2021
root:xnu-7195.101.1~3/RELEASE_X86_64 x86_64
=== Enabled user installed extensions ===
NuGet Package Management Extensions 0.26
NuGet Package Explorer 0.6
### Log File
<!--
1. Within Visual Studio:
a. Click **Tools** > **SDK Command Prompt** on macOS or
**Tools** > **Android** > **Android Adb Command Prompt** on Windows
b. On macOS, in the launched `Terminal.app` window, run:
adb logcat -d | pbcopy
On Windows, in the launched `cmd.exe` window, run:
adb logcat -d | clip
2. Paste below this comment block
-->
[Archiv.zip](https://github.com/xamarin/xamarin-android/files/6508444/Archiv.zip)
I'v added all my log files from %Home%/Library/Logs/VisualStudio/8.0
1. I removed all logs
2. Started VS
3. Open solution
4. Rebuild the Android project
5. Deploy to real device
6. Stuck
<!--
Switch to the "Preview" tab to ensure your issue renders correctly.
-->
| non_defect | deployment to physical android device stucks when fast assembly deployment is active vs mac steps to reproduce create a new xamarin forms solution ios and android open the android project options and enable the option fast assembly deployment for the build configuration debug click ok at this point there i recognize the first bug reopen now the android project options again and you will see that the option fast assembly deployment is disabled again but this is only a visual selection bug in the android csproj file the property is deleted which is ok embedassembliesintoapk missing fast assembly deployment on embedassembliesintoapk true fast assembly deployment off lets go ahead with the real issue now select your connected real android device in my case its a google pixel xl api the deployprocess is running but stops in the middle of task fast deploy application files now you can wait hours and nothing happens when you stop the deployment now and start it again vs is broken and will not build the project again it just stucks on building without any error you have to restart whole vs to be able to build again example project zip expected behavior should deploy to the device actual behavior stucks on deployment process version information on macos and within visual studio select visual studio about visual studio then click the show details button then click the copy information button paste below this comment block visual studio community for mac version build installation uuid gtk raleigh theme xamarin mac package version mono framework mdk runtime mono bit package version roslyn language service nuget version net core sdk sdk usr local share dotnet sdk sdks sdk versions msbuild sdks applications visual studio app contents resources lib monodevelop bin msbuild current bin sdks net core runtime runtime usr local share dotnet dotnet runtime versions net core sdk sdk xamarin profiler version location applications xamarin profiler app contents macos xamarin profiler updater version apple developer tools xcode build xamarin mac xamarin mac not installed can t find library frameworks xamarin mac framework versions current version xamarin ios version visual studio community hash branch build date xamarin designer version hash branch remotes origin build date utc xamarin android version visual studio community commit xamarin android android sdk users stefan library developer xamarin android sdk macosx supported android versions none installed sdk tools version sdk platform tools version sdk build tools version build information mono java interop xamarin java interop proguard guardsquare proguard sqlite xamarin sqlite xamarin android tools xamarin xamarin android tools microsoft openjdk for mobile java sdk users stefan library developer xamarin jdk microsoft dist openjdk android designer epl code available here android sdk manager version hash branch remotes origin dev bretjohn readme tweak build date utc android device manager version hash branch remotes origin dev jmt build date utc build information release id git revision build date build branch release xamarin extensions operating system mac os x darwin darwin kernel version fri mar pst root xnu release enabled user installed extensions nuget package management extensions nuget package explorer log file within visual studio a click tools sdk command prompt on macos or tools android android adb command prompt on windows b on macos in the launched terminal app window run adb logcat d pbcopy on windows in the launched cmd exe window run adb logcat d clip paste below this comment block i v added all my log files from home library logs visualstudio i removed all logs started vs open solution rebuild the android project deploy to real device stuck switch to the preview tab to ensure your issue renders correctly | 0 |
23,747 | 3,851,867,330 | IssuesEvent | 2016-04-06 05:28:43 | GPF/imame4all | https://api.github.com/repos/GPF/imame4all | closed | features suggestion | auto-migrated Priority-Medium Type-Defect | ```
force landscape
```
Original issue reported on code.google.com by `realc...@gmail.com` on 9 Apr 2012 at 11:39 | 1.0 | features suggestion - ```
force landscape
```
Original issue reported on code.google.com by `realc...@gmail.com` on 9 Apr 2012 at 11:39 | defect | features suggestion force landscape original issue reported on code google com by realc gmail com on apr at | 1 |
80,086 | 15,349,836,144 | IssuesEvent | 2021-03-01 00:34:51 | mjordan/islandora_workbench | https://api.github.com/repos/mjordan/islandora_workbench | opened | Move the "split_x_string()" functions from workbech_utils.py to their respective classes in workbench_fields.py | code cleanup | `split_link_string()`, `split_geolocation_string()`, and `split_typed_relation_string()` could be added to their respective field objects as `split_csv_string()`. | 1.0 | Move the "split_x_string()" functions from workbech_utils.py to their respective classes in workbench_fields.py - `split_link_string()`, `split_geolocation_string()`, and `split_typed_relation_string()` could be added to their respective field objects as `split_csv_string()`. | non_defect | move the split x string functions from workbech utils py to their respective classes in workbench fields py split link string split geolocation string and split typed relation string could be added to their respective field objects as split csv string | 0 |
142,222 | 13,018,202,434 | IssuesEvent | 2020-07-26 16:10:59 | alvaromontoro/gamepad-simulator | https://api.github.com/repos/alvaromontoro/gamepad-simulator | opened | Write initial documentation | documentation | - Improve the readme file
- Add documentation on how to use the module
Each subsequent change will need to include changes to the documentation too. | 1.0 | Write initial documentation - - Improve the readme file
- Add documentation on how to use the module
Each subsequent change will need to include changes to the documentation too. | non_defect | write initial documentation improve the readme file add documentation on how to use the module each subsequent change will need to include changes to the documentation too | 0 |
69,863 | 22,700,689,466 | IssuesEvent | 2022-07-05 10:21:33 | vector-im/element-android | https://api.github.com/repos/vector-im/element-android | opened | Thread: threads are not readable when there is no network | T-Defect | ### Steps to reproduce
1. Join a room with some thread
2. Open a thread: user can read messages of this thread
3. Go back to the main timeline
4. Enable airplane mode
5. The banner "Airplane mode is on" is displayed on the main timeline
6. Open the same thread than at step 2
### Outcome
#### What did you expect?
I can read the messages from the thread, they are loaded in the DB (cache).
#### What happened instead?
Empty screen, with infinite loading, restarting forever (so not really the same thing that infinite loading), looping to try to get the messages
Note that the airplane mode banner is displayed, so this is mitigating this issue.
### Your phone model
any
### Operating system version
any
### Application version and app store
1.4.16
### Homeserver
any
### Will you send logs?
No
### Are you willing to provide a PR?
No | 1.0 | Thread: threads are not readable when there is no network - ### Steps to reproduce
1. Join a room with some thread
2. Open a thread: user can read messages of this thread
3. Go back to the main timeline
4. Enable airplane mode
5. The banner "Airplane mode is on" is displayed on the main timeline
6. Open the same thread than at step 2
### Outcome
#### What did you expect?
I can read the messages from the thread, they are loaded in the DB (cache).
#### What happened instead?
Empty screen, with infinite loading, restarting forever (so not really the same thing that infinite loading), looping to try to get the messages
Note that the airplane mode banner is displayed, so this is mitigating this issue.
### Your phone model
any
### Operating system version
any
### Application version and app store
1.4.16
### Homeserver
any
### Will you send logs?
No
### Are you willing to provide a PR?
No | defect | thread threads are not readable when there is no network steps to reproduce join a room with some thread open a thread user can read messages of this thread go back to the main timeline enable airplane mode the banner airplane mode is on is displayed on the main timeline open the same thread than at step outcome what did you expect i can read the messages from the thread they are loaded in the db cache what happened instead empty screen with infinite loading restarting forever so not really the same thing that infinite loading looping to try to get the messages note that the airplane mode banner is displayed so this is mitigating this issue your phone model any operating system version any application version and app store homeserver any will you send logs no are you willing to provide a pr no | 1 |
1,031 | 4,827,518,233 | IssuesEvent | 2016-11-07 13:53:11 | ansible/ansible-modules-extras | https://api.github.com/repos/ansible/ansible-modules-extras | closed | Consul module idempotency | affects_2.3 feature_idea waiting_on_maintainer | Hey guys! I wonder if anyone can provide a bit of insight into this comment:
https://github.com/ansible/ansible-modules-extras/blob/fdb4a58f975fc4df4b22157b97428b0b274a0d3d/clustering/consul.py#L33-L38
Was hoping I could help further that effort along on either the consul or the ansible side, but after some searching im not able to find much news about this upcoming api :(
Maybe @sgargan can help? Thanks so much in advance!
| True | Consul module idempotency - Hey guys! I wonder if anyone can provide a bit of insight into this comment:
https://github.com/ansible/ansible-modules-extras/blob/fdb4a58f975fc4df4b22157b97428b0b274a0d3d/clustering/consul.py#L33-L38
Was hoping I could help further that effort along on either the consul or the ansible side, but after some searching im not able to find much news about this upcoming api :(
Maybe @sgargan can help? Thanks so much in advance!
| non_defect | consul module idempotency hey guys i wonder if anyone can provide a bit of insight into this comment was hoping i could help further that effort along on either the consul or the ansible side but after some searching im not able to find much news about this upcoming api maybe sgargan can help thanks so much in advance | 0 |
57,638 | 15,888,672,201 | IssuesEvent | 2021-04-10 08:27:04 | naev/naev | https://api.github.com/repos/naev/naev | closed | graphic novel dialogue not alwas readable | Priority-High Type-Defect | When I was bringing Dr Strangelove the Nebula Artifact recovered from the feral drone, I had the game running in a window
with a border on top, underneath a xfce menue bar on a loptop with 768p squatscreen. When the dialogue was a bit longer, the bottom was cut off.
That wouldn't have been such a bad thing if I could have used F11 to switch to full screen, but alas, that key is also
intercepted by the graphic novel handling, so the only way is to somehow quit the game, load from backup, switch to full-screen,
eliminate the feral drone again, and bring the Nebula Artifact to Dr Strangelove again. | 1.0 | graphic novel dialogue not alwas readable - When I was bringing Dr Strangelove the Nebula Artifact recovered from the feral drone, I had the game running in a window
with a border on top, underneath a xfce menue bar on a loptop with 768p squatscreen. When the dialogue was a bit longer, the bottom was cut off.
That wouldn't have been such a bad thing if I could have used F11 to switch to full screen, but alas, that key is also
intercepted by the graphic novel handling, so the only way is to somehow quit the game, load from backup, switch to full-screen,
eliminate the feral drone again, and bring the Nebula Artifact to Dr Strangelove again. | defect | graphic novel dialogue not alwas readable when i was bringing dr strangelove the nebula artifact recovered from the feral drone i had the game running in a window with a border on top underneath a xfce menue bar on a loptop with squatscreen when the dialogue was a bit longer the bottom was cut off that wouldn t have been such a bad thing if i could have used to switch to full screen but alas that key is also intercepted by the graphic novel handling so the only way is to somehow quit the game load from backup switch to full screen eliminate the feral drone again and bring the nebula artifact to dr strangelove again | 1 |
120,325 | 12,066,553,858 | IssuesEvent | 2020-04-16 11:58:38 | sebastian-brunner/test_issue_mover_with_pr | https://api.github.com/repos/sebastian-brunner/test_issue_mover_with_pr | opened | test issue 2 | documentation enhancement |
Originally created by @sebastian-brunner (sebastian.brunner@dlr.de) at 2020-04-14 14:59:31+00:00 (moved from RMC internal repository) | 1.0 | test issue 2 -
Originally created by @sebastian-brunner (sebastian.brunner@dlr.de) at 2020-04-14 14:59:31+00:00 (moved from RMC internal repository) | non_defect | test issue originally created by sebastian brunner sebastian brunner dlr de at moved from rmc internal repository | 0 |
16,452 | 2,899,788,171 | IssuesEvent | 2015-06-17 13:30:00 | compomics/pride-asa-pipeline | https://api.github.com/repos/compomics/pride-asa-pipeline | closed | GUI doens't launch | auto-migrated Priority-Medium Type-Defect | ```
Just downloaded and unzipped the file.
Typing "java -jar pride-asa-pipeline-1.5.6.jar" or double clicking on the jar
file
won't start the application.
Error message is attached.
Could it be a version conflict or missing libs?
Config
Ubuntu 10.04, 64bits
java version "1.6.0_27"
OpenJDK Runtime Environment (IcedTea6 1.12.3) (6b27-1.12.3-0ubuntu1~10.04.1)
OpenJDK 64-Bit Server VM (build 20.0-b12, mixed mode)
```
Original issue reported on code.google.com by `Christin...@qimr.edu.au` on 24 Apr 2013 at 5:08
Attachments:
* [error.log](https://storage.googleapis.com/google-code-attachments/pride-asa-pipeline/issue-1/comment-0/error.log)
* [pride-asa-pipeline.log](https://storage.googleapis.com/google-code-attachments/pride-asa-pipeline/issue-1/comment-0/pride-asa-pipeline.log)
| 1.0 | GUI doens't launch - ```
Just downloaded and unzipped the file.
Typing "java -jar pride-asa-pipeline-1.5.6.jar" or double clicking on the jar
file
won't start the application.
Error message is attached.
Could it be a version conflict or missing libs?
Config
Ubuntu 10.04, 64bits
java version "1.6.0_27"
OpenJDK Runtime Environment (IcedTea6 1.12.3) (6b27-1.12.3-0ubuntu1~10.04.1)
OpenJDK 64-Bit Server VM (build 20.0-b12, mixed mode)
```
Original issue reported on code.google.com by `Christin...@qimr.edu.au` on 24 Apr 2013 at 5:08
Attachments:
* [error.log](https://storage.googleapis.com/google-code-attachments/pride-asa-pipeline/issue-1/comment-0/error.log)
* [pride-asa-pipeline.log](https://storage.googleapis.com/google-code-attachments/pride-asa-pipeline/issue-1/comment-0/pride-asa-pipeline.log)
| defect | gui doens t launch just downloaded and unzipped the file typing java jar pride asa pipeline jar or double clicking on the jar file won t start the application error message is attached could it be a version conflict or missing libs config ubuntu java version openjdk runtime environment openjdk bit server vm build mixed mode original issue reported on code google com by christin qimr edu au on apr at attachments | 1 |
101,697 | 8,794,219,283 | IssuesEvent | 2018-12-22 00:04:07 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Failing test: UI Functional Tests.test/functional/apps/visualize/_pie_chart·js - visualize app pie chart other bucket should apply correct filter on other bucket | :KibanaApp failed-test | A test failed on a tracked branch
```
{ [POST http://localhost:9515/session/7b14977593ec30abc03dbc9ce5f840e1/execute / {"script":"return arguments[0].getAttribute(arguments[1]);","args":[{"ELEMENT":"0.5683948932143932-31"},"data-label"]}] stale element reference: element is not attached to the page document
(Session info: headless chrome=70.0.3538.110)
(Driver info: chromedriver=2.42.591071 (0b695ff80972cc1a65a5cd643186d2ae582cd4ac),platform=Linux 3.10.0-862.14.4.el7.x86_64 x86_64)
at Server._post (test/functional/services/remote/verbose_remote_logging.js:34:21)
at runRequest (node_modules/leadfoot/Session.js:92:40)
at getFinalValue (node_modules/dojo/_debug/Promise.ts:462:22)
at node_modules/dojo/_debug/Promise.ts:478:11
at node_modules/dojo/_debug/Promise.ts:393:16
at runCallbacks (node_modules/dojo/_debug/Promise.ts:11:12)
at node_modules/dojo/_debug/Promise.ts:317:5
at run (node_modules/dojo/_debug/Promise.ts:237:8)
at node_modules/dojo/_debug/nextTick.ts:44:4
at _combinedTickCallback (internal/process/next_tick.js:131:7)
at process._tickCallback (internal/process/next_tick.js:180:9)
name: 'StaleElementReference',
message: '[POST http://localhost:9515/session/7b14977593ec30abc03dbc9ce5f840e1/execute / {"script":"return arguments[0].getAttribute(arguments[1]);","args":[{"ELEMENT":"0.5683948932143932-31"},"data-label"]}] stale element reference: element is not attached to the page document\n (Session info: headless chrome=70.0.3538.110)\n (Driver info: chromedriver=2.42.591071 (0b695ff80972cc1a65a5cd643186d2ae582cd4ac),platform=Linux 3.10.0-862.14.4.el7.x86_64 x86_64)',
status: 10,
detail:
{ message: 'stale element reference: element is not attached to the page document\n (Session info: headless chrome=70.0.3538.110)\n (Driver info: chromedriver=2.42.591071 (0b695ff80972cc1a65a5cd643186d2ae582cd4ac),platform=Linux 3.10.0-862.14.4.el7.x86_64 x86_64)' },
request:
{ url: 'http://localhost:9515/session/7b14977593ec30abc03dbc9ce5f840e1/execute',
method: 'POST',
data:
{ script: 'return arguments[0].getAttribute(arguments[1]);',
args: [Array] } },
response:
{ data: <Buffer 7b 22 73 65 73 73 69 6f 6e 49 64 22 3a 22 37 62 31 34 39 37 37 35 39 33 65 63 33 30 61 62 63 30 33 64 62 63 39 63 65 35 66 38 34 30 65 31 22 2c 22 73 ... >,
getHeader: [Function: getHeader],
requestOptions:
{ followRedirects: false,
handleAs: 'text',
headers: [Object],
method: 'POST',
data: '{"script":"return arguments[0].getAttribute(arguments[1]);","args":[{"ELEMENT":"0.5683948932143932-31"},"data-label"]}' },
statusCode: 200,
url: 'http://localhost:9515/session/7b14977593ec30abc03dbc9ce5f840e1/execute',
nativeResponse:
IncomingMessage {
_readableState: [Object],
readable: false,
domain: null,
_events: [Object],
_eventsCount: 2,
_maxListeners: undefined,
socket: [Object],
connection: [Object],
httpVersionMajor: 1,
httpVersionMinor: 1,
httpVersion: '1.1',
complete: true,
headers: [Object],
rawHeaders: [Array],
trailers: {},
rawTrailers: [],
upgrade: false,
url: '',
method: null,
statusCode: 200,
statusMessage: 'OK',
client: [Object],
_consuming: true,
_dumped: false,
req: [Object],
read: [Function] } } }
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+6.x/JOB=kibana-ciGroup11,node=immutable/119/)
<!-- kibanaCiData = {"failed-test":{"test.class":"UI Functional Tests.test/functional/apps/visualize/_pie_chart·js","test.name":"visualize app pie chart other bucket should apply correct filter on other bucket","test.failCount":3}} --> | 1.0 | Failing test: UI Functional Tests.test/functional/apps/visualize/_pie_chart·js - visualize app pie chart other bucket should apply correct filter on other bucket - A test failed on a tracked branch
```
{ [POST http://localhost:9515/session/7b14977593ec30abc03dbc9ce5f840e1/execute / {"script":"return arguments[0].getAttribute(arguments[1]);","args":[{"ELEMENT":"0.5683948932143932-31"},"data-label"]}] stale element reference: element is not attached to the page document
(Session info: headless chrome=70.0.3538.110)
(Driver info: chromedriver=2.42.591071 (0b695ff80972cc1a65a5cd643186d2ae582cd4ac),platform=Linux 3.10.0-862.14.4.el7.x86_64 x86_64)
at Server._post (test/functional/services/remote/verbose_remote_logging.js:34:21)
at runRequest (node_modules/leadfoot/Session.js:92:40)
at getFinalValue (node_modules/dojo/_debug/Promise.ts:462:22)
at node_modules/dojo/_debug/Promise.ts:478:11
at node_modules/dojo/_debug/Promise.ts:393:16
at runCallbacks (node_modules/dojo/_debug/Promise.ts:11:12)
at node_modules/dojo/_debug/Promise.ts:317:5
at run (node_modules/dojo/_debug/Promise.ts:237:8)
at node_modules/dojo/_debug/nextTick.ts:44:4
at _combinedTickCallback (internal/process/next_tick.js:131:7)
at process._tickCallback (internal/process/next_tick.js:180:9)
name: 'StaleElementReference',
message: '[POST http://localhost:9515/session/7b14977593ec30abc03dbc9ce5f840e1/execute / {"script":"return arguments[0].getAttribute(arguments[1]);","args":[{"ELEMENT":"0.5683948932143932-31"},"data-label"]}] stale element reference: element is not attached to the page document\n (Session info: headless chrome=70.0.3538.110)\n (Driver info: chromedriver=2.42.591071 (0b695ff80972cc1a65a5cd643186d2ae582cd4ac),platform=Linux 3.10.0-862.14.4.el7.x86_64 x86_64)',
status: 10,
detail:
{ message: 'stale element reference: element is not attached to the page document\n (Session info: headless chrome=70.0.3538.110)\n (Driver info: chromedriver=2.42.591071 (0b695ff80972cc1a65a5cd643186d2ae582cd4ac),platform=Linux 3.10.0-862.14.4.el7.x86_64 x86_64)' },
request:
{ url: 'http://localhost:9515/session/7b14977593ec30abc03dbc9ce5f840e1/execute',
method: 'POST',
data:
{ script: 'return arguments[0].getAttribute(arguments[1]);',
args: [Array] } },
response:
{ data: <Buffer 7b 22 73 65 73 73 69 6f 6e 49 64 22 3a 22 37 62 31 34 39 37 37 35 39 33 65 63 33 30 61 62 63 30 33 64 62 63 39 63 65 35 66 38 34 30 65 31 22 2c 22 73 ... >,
getHeader: [Function: getHeader],
requestOptions:
{ followRedirects: false,
handleAs: 'text',
headers: [Object],
method: 'POST',
data: '{"script":"return arguments[0].getAttribute(arguments[1]);","args":[{"ELEMENT":"0.5683948932143932-31"},"data-label"]}' },
statusCode: 200,
url: 'http://localhost:9515/session/7b14977593ec30abc03dbc9ce5f840e1/execute',
nativeResponse:
IncomingMessage {
_readableState: [Object],
readable: false,
domain: null,
_events: [Object],
_eventsCount: 2,
_maxListeners: undefined,
socket: [Object],
connection: [Object],
httpVersionMajor: 1,
httpVersionMinor: 1,
httpVersion: '1.1',
complete: true,
headers: [Object],
rawHeaders: [Array],
trailers: {},
rawTrailers: [],
upgrade: false,
url: '',
method: null,
statusCode: 200,
statusMessage: 'OK',
client: [Object],
_consuming: true,
_dumped: false,
req: [Object],
read: [Function] } } }
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+6.x/JOB=kibana-ciGroup11,node=immutable/119/)
<!-- kibanaCiData = {"failed-test":{"test.class":"UI Functional Tests.test/functional/apps/visualize/_pie_chart·js","test.name":"visualize app pie chart other bucket should apply correct filter on other bucket","test.failCount":3}} --> | non_defect | failing test ui functional tests test functional apps visualize pie chart·js visualize app pie chart other bucket should apply correct filter on other bucket a test failed on a tracked branch getattribute arguments args stale element reference element is not attached to the page document session info headless chrome driver info chromedriver platform linux at server post test functional services remote verbose remote logging js at runrequest node modules leadfoot session js at getfinalvalue node modules dojo debug promise ts at node modules dojo debug promise ts at node modules dojo debug promise ts at runcallbacks node modules dojo debug promise ts at node modules dojo debug promise ts at run node modules dojo debug promise ts at node modules dojo debug nexttick ts at combinedtickcallback internal process next tick js at process tickcallback internal process next tick js name staleelementreference message getattribute arguments args stale element reference element is not attached to the page document n session info headless chrome n driver info chromedriver platform linux status detail message stale element reference element is not attached to the page document n session info headless chrome n driver info chromedriver platform linux request url method post data script return arguments getattribute arguments args response data getheader requestoptions followredirects false handleas text headers method post data script return arguments getattribute arguments args statuscode url nativeresponse incomingmessage readablestate readable false domain null events eventscount maxlisteners undefined socket connection httpversionmajor httpversionminor httpversion complete true headers rawheaders trailers rawtrailers upgrade false url method null statuscode statusmessage ok client consuming true dumped false req read first failure | 0 |
7,694 | 5,143,473,902 | IssuesEvent | 2017-01-12 16:05:11 | Yakindu/statecharts | https://api.github.com/repos/Yakindu/statecharts | opened | Change default transition layouting to rectilinear | is-Usability-Issue | Rectilinear layouting provides a much more robust style of rendering transitions, as the angle values of the bendpoints will always stay at 90°
Manually adjusted obligue transitions change the angle values of their bendpoints to unexpected/unwated degrees when model elements are changed/added/resized. This can cause a visually unappealing result. | True | Change default transition layouting to rectilinear - Rectilinear layouting provides a much more robust style of rendering transitions, as the angle values of the bendpoints will always stay at 90°
Manually adjusted obligue transitions change the angle values of their bendpoints to unexpected/unwated degrees when model elements are changed/added/resized. This can cause a visually unappealing result. | non_defect | change default transition layouting to rectilinear rectilinear layouting provides a much more robust style of rendering transitions as the angle values of the bendpoints will always stay at ° manually adjusted obligue transitions change the angle values of their bendpoints to unexpected unwated degrees when model elements are changed added resized this can cause a visually unappealing result | 0 |
101,850 | 4,146,549,410 | IssuesEvent | 2016-06-15 00:42:33 | marliseu/cs50xapp | https://api.github.com/repos/marliseu/cs50xapp | closed | Sorted Cohort Directory | Enhancement Medium Priority | Sort arrays of users by first name in:
- Directory.php
- Grades.php | 1.0 | Sorted Cohort Directory - Sort arrays of users by first name in:
- Directory.php
- Grades.php | non_defect | sorted cohort directory sort arrays of users by first name in directory php grades php | 0 |
49,432 | 13,186,710,182 | IssuesEvent | 2020-08-13 01:03:58 | icecube-trac/tix3 | https://api.github.com/repos/icecube-trac/tix3 | opened | muongun - cubature.c lack code coverage / tests (Trac #1375) | Incomplete Migration Migrated from Trac combo simulation defect | <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1375">https://code.icecube.wisc.edu/ticket/1375</a>, reported by nega and owned by jvansanten</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2016-03-18T21:14:07",
"description": "http://software.icecube.wisc.edu/coverage/00_LATEST/MuonGun/private/cubature/\n\nIf a file is important enough to import from another project into our code base, it's important enough to have tests and coverage applied to it.",
"reporter": "nega",
"cc": "",
"resolution": "fixed",
"_ts": "1458335647931556",
"component": "combo simulation",
"summary": "muongun - cubature.c lack code coverage / tests",
"priority": "normal",
"keywords": "",
"time": "2015-10-01T13:59:56",
"milestone": "",
"owner": "jvansanten",
"type": "defect"
}
```
</p>
</details>
| 1.0 | muongun - cubature.c lack code coverage / tests (Trac #1375) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1375">https://code.icecube.wisc.edu/ticket/1375</a>, reported by nega and owned by jvansanten</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2016-03-18T21:14:07",
"description": "http://software.icecube.wisc.edu/coverage/00_LATEST/MuonGun/private/cubature/\n\nIf a file is important enough to import from another project into our code base, it's important enough to have tests and coverage applied to it.",
"reporter": "nega",
"cc": "",
"resolution": "fixed",
"_ts": "1458335647931556",
"component": "combo simulation",
"summary": "muongun - cubature.c lack code coverage / tests",
"priority": "normal",
"keywords": "",
"time": "2015-10-01T13:59:56",
"milestone": "",
"owner": "jvansanten",
"type": "defect"
}
```
</p>
</details>
| defect | muongun cubature c lack code coverage tests trac migrated from json status closed changetime description a file is important enough to import from another project into our code base it s important enough to have tests and coverage applied to it reporter nega cc resolution fixed ts component combo simulation summary muongun cubature c lack code coverage tests priority normal keywords time milestone owner jvansanten type defect | 1 |
210,789 | 7,194,718,487 | IssuesEvent | 2018-02-04 08:59:08 | FACN3/easyRep | https://api.github.com/repos/FACN3/easyRep | opened | Create a Report Form | T1d priority-3 technical | As a user I would like to:
- Write a description of the situation.
- Be able to provide a picture or other Media about the issue.
- Be able to send the report to the appropriate authorities.
Acceptance criteria:
- [ ] A text input for description.
- [ ] A button for uploading Media.
- [ ] A send button for reporting. | 1.0 | Create a Report Form - As a user I would like to:
- Write a description of the situation.
- Be able to provide a picture or other Media about the issue.
- Be able to send the report to the appropriate authorities.
Acceptance criteria:
- [ ] A text input for description.
- [ ] A button for uploading Media.
- [ ] A send button for reporting. | non_defect | create a report form as a user i would like to write a description of the situation be able to provide a picture or other media about the issue be able to send the report to the appropriate authorities acceptance criteria a text input for description a button for uploading media a send button for reporting | 0 |
58,303 | 16,480,954,009 | IssuesEvent | 2021-05-24 11:33:07 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | closed | No DataSerializerFactory registered for namespace: -2000 (version 4.1 - as Hibernate 2nd level cache - native client mode - using HazelcastLocalCacheRegionFactory) | Source: Community Team: Integration Type: Defect | Hello,
I am trying to use Hazelcast 4.1 as Hibernate's 2nd level cache provider in native client mode, I installed Hazelcast cluster v 4.1 from the corresponding docker image without any specific serialization configuration.
my persistence.xml related properties look like this:
```xml
<property name="hibernate.cache.use_second_level_cache" value="true"/>
<property name="hibernate.cache.use_query_cache" value="true"/>
<property name="hibernate.cache.region.factory_class" value="com.hazelcast.hibernate.HazelcastLocalCacheRegionFactory"/>
<property name="hibernate.session_factory_name" value="com.hazelcast.hibernate.HazelcastLocalCacheRegionFactory"/>
<property name="hibernate.cache.hazelcast.use_native_client" value="true"/>
<property name="hibernate.cache.hazelcast.native_client_address" value="127.0.0.1:5701"/>
<property name="hibernate.cache.hazelcast.native_client_group" value="dev"/>
<property name="hibernate.cache.hazelcast.native_client_password" value=""/>
```
Note: I am deploying the app on Payara Server V5.2021.2
the application is running successfully and the invalidation topics are created on the Hazelcast cluster side, but whenever any entity is created/updated I get this exception:
```yaml
hz.client_1 [dev] [4.1] hz.client_1.event-9 caught an exception while processing:com.hazelcast.client.impl.spi.impl.listener.ClientListenerServiceImpl$ClientEventProcessor@35eb4fba
com.hazelcast.nio.serialization.HazelcastSerializationException: No DataSerializerFactory registered for namespace: -2000
at com.hazelcast.internal.serialization.impl.DataSerializableSerializer.readInternal(DataSerializableSerializer.java:139)
at com.hazelcast.internal.serialization.impl.DataSerializableSerializer.read(DataSerializableSerializer.java:106)
at com.hazelcast.internal.serialization.impl.DataSerializableSerializer.read(DataSerializableSerializer.java:51)
at com.hazelcast.internal.serialization.impl.StreamSerializerAdapter.read(StreamSerializerAdapter.java:44)
at com.hazelcast.internal.serialization.impl.AbstractSerializationService.toObject(AbstractSerializationService.java:205)
at com.hazelcast.topic.impl.DataAwareMessage.getMessageObject(DataAwareMessage.java:44)
at com.hazelcast.hibernate.local.LocalRegionCache.lambda$createMessageListener$0(LocalRegionCache.java:247)
at com.hazelcast.client.impl.proxy.ClientTopicProxy$TopicItemHandler.handleTopicEvent(ClientTopicProxy.java:132)
at com.hazelcast.client.impl.protocol.codec.TopicAddMessageListenerCodec$AbstractEventHandler.handle(TopicAddMessageListenerCodec.java:139)
at com.hazelcast.client.impl.proxy.ClientTopicProxy$TopicItemHandler.handle(ClientTopicProxy.java:120)
at com.hazelcast.client.impl.spi.impl.listener.ClientListenerServiceImpl.handleEventMessageOnCallingThread(ClientListenerServiceImpl.java:189)
at com.hazelcast.client.impl.spi.impl.listener.ClientListenerServiceImpl$ClientEventProcessor.run(ClientListenerServiceImpl.java:356)
at com.hazelcast.internal.util.executor.StripedExecutor$Worker.process(StripedExecutor.java:245)
at com.hazelcast.internal.util.executor.StripedExecutor$Worker.run(StripedExecutor.java:228)
```
**Libraries:**
Hibernate:5.4.12.Final
hazelcast:4.1
hazelcast-hibernate53:2.2.0
**Environment:**
JDK 11
Payara Server 5.2021.2
no exceptions in the Hazelcast cluster's log.
Thanks, | 1.0 | No DataSerializerFactory registered for namespace: -2000 (version 4.1 - as Hibernate 2nd level cache - native client mode - using HazelcastLocalCacheRegionFactory) - Hello,
I am trying to use Hazelcast 4.1 as Hibernate's 2nd level cache provider in native client mode, I installed Hazelcast cluster v 4.1 from the corresponding docker image without any specific serialization configuration.
my persistence.xml related properties look like this:
```xml
<property name="hibernate.cache.use_second_level_cache" value="true"/>
<property name="hibernate.cache.use_query_cache" value="true"/>
<property name="hibernate.cache.region.factory_class" value="com.hazelcast.hibernate.HazelcastLocalCacheRegionFactory"/>
<property name="hibernate.session_factory_name" value="com.hazelcast.hibernate.HazelcastLocalCacheRegionFactory"/>
<property name="hibernate.cache.hazelcast.use_native_client" value="true"/>
<property name="hibernate.cache.hazelcast.native_client_address" value="127.0.0.1:5701"/>
<property name="hibernate.cache.hazelcast.native_client_group" value="dev"/>
<property name="hibernate.cache.hazelcast.native_client_password" value=""/>
```
Note: I am deploying the app on Payara Server V5.2021.2
the application is running successfully and the invalidation topics are created on the Hazelcast cluster side, but whenever any entity is created/updated I get this exception:
```yaml
hz.client_1 [dev] [4.1] hz.client_1.event-9 caught an exception while processing:com.hazelcast.client.impl.spi.impl.listener.ClientListenerServiceImpl$ClientEventProcessor@35eb4fba
com.hazelcast.nio.serialization.HazelcastSerializationException: No DataSerializerFactory registered for namespace: -2000
at com.hazelcast.internal.serialization.impl.DataSerializableSerializer.readInternal(DataSerializableSerializer.java:139)
at com.hazelcast.internal.serialization.impl.DataSerializableSerializer.read(DataSerializableSerializer.java:106)
at com.hazelcast.internal.serialization.impl.DataSerializableSerializer.read(DataSerializableSerializer.java:51)
at com.hazelcast.internal.serialization.impl.StreamSerializerAdapter.read(StreamSerializerAdapter.java:44)
at com.hazelcast.internal.serialization.impl.AbstractSerializationService.toObject(AbstractSerializationService.java:205)
at com.hazelcast.topic.impl.DataAwareMessage.getMessageObject(DataAwareMessage.java:44)
at com.hazelcast.hibernate.local.LocalRegionCache.lambda$createMessageListener$0(LocalRegionCache.java:247)
at com.hazelcast.client.impl.proxy.ClientTopicProxy$TopicItemHandler.handleTopicEvent(ClientTopicProxy.java:132)
at com.hazelcast.client.impl.protocol.codec.TopicAddMessageListenerCodec$AbstractEventHandler.handle(TopicAddMessageListenerCodec.java:139)
at com.hazelcast.client.impl.proxy.ClientTopicProxy$TopicItemHandler.handle(ClientTopicProxy.java:120)
at com.hazelcast.client.impl.spi.impl.listener.ClientListenerServiceImpl.handleEventMessageOnCallingThread(ClientListenerServiceImpl.java:189)
at com.hazelcast.client.impl.spi.impl.listener.ClientListenerServiceImpl$ClientEventProcessor.run(ClientListenerServiceImpl.java:356)
at com.hazelcast.internal.util.executor.StripedExecutor$Worker.process(StripedExecutor.java:245)
at com.hazelcast.internal.util.executor.StripedExecutor$Worker.run(StripedExecutor.java:228)
```
**Libraries:**
Hibernate:5.4.12.Final
hazelcast:4.1
hazelcast-hibernate53:2.2.0
**Environment:**
JDK 11
Payara Server 5.2021.2
no exceptions in the Hazelcast cluster's log.
Thanks, | defect | no dataserializerfactory registered for namespace version as hibernate level cache native client mode using hazelcastlocalcacheregionfactory hello i am trying to use hazelcast as hibernate s level cache provider in native client mode i installed hazelcast cluster v from the corresponding docker image without any specific serialization configuration my persistence xml related properties look like this xml note i am deploying the app on payara server the application is running successfully and the invalidation topics are created on the hazelcast cluster side but whenever any entity is created updated i get this exception yaml hz client hz client event caught an exception while processing com hazelcast client impl spi impl listener clientlistenerserviceimpl clienteventprocessor com hazelcast nio serialization hazelcastserializationexception no dataserializerfactory registered for namespace at com hazelcast internal serialization impl dataserializableserializer readinternal dataserializableserializer java at com hazelcast internal serialization impl dataserializableserializer read dataserializableserializer java at com hazelcast internal serialization impl dataserializableserializer read dataserializableserializer java at com hazelcast internal serialization impl streamserializeradapter read streamserializeradapter java at com hazelcast internal serialization impl abstractserializationservice toobject abstractserializationservice java at com hazelcast topic impl dataawaremessage getmessageobject dataawaremessage java at com hazelcast hibernate local localregioncache lambda createmessagelistener localregioncache java at com hazelcast client impl proxy clienttopicproxy topicitemhandler handletopicevent clienttopicproxy java at com hazelcast client impl protocol codec topicaddmessagelistenercodec abstracteventhandler handle topicaddmessagelistenercodec java at com hazelcast client impl proxy clienttopicproxy topicitemhandler handle clienttopicproxy java at com hazelcast client impl spi impl listener clientlistenerserviceimpl handleeventmessageoncallingthread clientlistenerserviceimpl java at com hazelcast client impl spi impl listener clientlistenerserviceimpl clienteventprocessor run clientlistenerserviceimpl java at com hazelcast internal util executor stripedexecutor worker process stripedexecutor java at com hazelcast internal util executor stripedexecutor worker run stripedexecutor java libraries hibernate final hazelcast hazelcast environment jdk payara server no exceptions in the hazelcast cluster s log thanks | 1 |
2,910 | 2,607,965,808 | IssuesEvent | 2015-02-26 00:42:17 | chrsmithdemos/leveldb | https://api.github.com/repos/chrsmithdemos/leveldb | closed | corruption_test failed: db/corruption_test.cc:325: failed: 1 == 5 | auto-migrated Priority-Medium Type-Defect | ```
What steps will reproduce the problem?
1. make corruption_test
2. for((i=1;;i++)); do
./corruption_test
if [[ $? -ne 0 ]]; then
break;
fi
done
3.
What is the expected output? What do you see instead?
Expected output:
==== Test CorruptionTest.Recovery
expected=100..100; got=100; bad_keys=0; bad_values=0; missed=0
expected=36..36; got=36; bad_keys=0; bad_values=0; missed=64
==== Test CorruptionTest.RecoverWriteError
==== Test CorruptionTest.NewFileErrorDuringWrite
==== Test CorruptionTest.TableFile
expected=99..99; got=99; bad_keys=0; bad_values=1; missed=0
==== Test CorruptionTest.TableFileIndexData
expected=5000..9999; got=7958; bad_keys=0; bad_values=0; missed=0
==== Test CorruptionTest.MissingDescriptor
expected=1000..1000; got=1000; bad_keys=0; bad_values=0; missed=0
==== Test CorruptionTest.SequenceNumberRecovery
==== Test CorruptionTest.CorruptedDescriptor
==== Test CorruptionTest.CompactionInputError
expected=9..9; got=9; bad_keys=0; bad_values=1; missed=0
expected=10000..10000; got=10000; bad_keys=0; bad_values=0; missed=0
==== Test CorruptionTest.CompactionInputErrorParanoid
expected=9..9; got=9; bad_keys=2; bad_values=1; missed=0
==== Test CorruptionTest.UnrelatedKeys
==== PASSED 11 tests
What I see:
==== Test CorruptionTest.Recovery
expected=100..100; got=100; bad_keys=0; bad_values=0; missed=0
expected=36..36; got=36; bad_keys=0; bad_values=0; missed=64
==== Test CorruptionTest.RecoverWriteError
==== Test CorruptionTest.NewFileErrorDuringWrite
==== Test CorruptionTest.TableFile
expected=99..99; got=99; bad_keys=0; bad_values=1; missed=0
==== Test CorruptionTest.TableFileIndexData
expected=5000..9999; got=7958; bad_keys=0; bad_values=0; missed=0
==== Test CorruptionTest.MissingDescriptor
expected=1000..1000; got=1000; bad_keys=0; bad_values=0; missed=0
==== Test CorruptionTest.SequenceNumberRecovery
==== Test CorruptionTest.CorruptedDescriptor
==== Test CorruptionTest.CompactionInputError
expected=9..9; got=9; bad_keys=0; bad_values=1; missed=0
expected=10000..10000; got=10000; bad_keys=0; bad_values=0; missed=0
==== Test CorruptionTest.CompactionInputErrorParanoid
db/corruption_test.cc:325: failed: 1 == 5
What version of the product are you using? On what operating system?
1.4, git commit "85584d497e7b354853b72f450683d59fcf6b9c5c"
OS: CentOS 5.4, kernel 2.6.35.13, x64 virtual machine(VMWare)
Please provide any additional information below.
```
-----
Original issue reported on code.google.com by `tfengjun` on 7 May 2012 at 6:21 | 1.0 | corruption_test failed: db/corruption_test.cc:325: failed: 1 == 5 - ```
What steps will reproduce the problem?
1. make corruption_test
2. for((i=1;;i++)); do
./corruption_test
if [[ $? -ne 0 ]]; then
break;
fi
done
3.
What is the expected output? What do you see instead?
Expected output:
==== Test CorruptionTest.Recovery
expected=100..100; got=100; bad_keys=0; bad_values=0; missed=0
expected=36..36; got=36; bad_keys=0; bad_values=0; missed=64
==== Test CorruptionTest.RecoverWriteError
==== Test CorruptionTest.NewFileErrorDuringWrite
==== Test CorruptionTest.TableFile
expected=99..99; got=99; bad_keys=0; bad_values=1; missed=0
==== Test CorruptionTest.TableFileIndexData
expected=5000..9999; got=7958; bad_keys=0; bad_values=0; missed=0
==== Test CorruptionTest.MissingDescriptor
expected=1000..1000; got=1000; bad_keys=0; bad_values=0; missed=0
==== Test CorruptionTest.SequenceNumberRecovery
==== Test CorruptionTest.CorruptedDescriptor
==== Test CorruptionTest.CompactionInputError
expected=9..9; got=9; bad_keys=0; bad_values=1; missed=0
expected=10000..10000; got=10000; bad_keys=0; bad_values=0; missed=0
==== Test CorruptionTest.CompactionInputErrorParanoid
expected=9..9; got=9; bad_keys=2; bad_values=1; missed=0
==== Test CorruptionTest.UnrelatedKeys
==== PASSED 11 tests
What I see:
==== Test CorruptionTest.Recovery
expected=100..100; got=100; bad_keys=0; bad_values=0; missed=0
expected=36..36; got=36; bad_keys=0; bad_values=0; missed=64
==== Test CorruptionTest.RecoverWriteError
==== Test CorruptionTest.NewFileErrorDuringWrite
==== Test CorruptionTest.TableFile
expected=99..99; got=99; bad_keys=0; bad_values=1; missed=0
==== Test CorruptionTest.TableFileIndexData
expected=5000..9999; got=7958; bad_keys=0; bad_values=0; missed=0
==== Test CorruptionTest.MissingDescriptor
expected=1000..1000; got=1000; bad_keys=0; bad_values=0; missed=0
==== Test CorruptionTest.SequenceNumberRecovery
==== Test CorruptionTest.CorruptedDescriptor
==== Test CorruptionTest.CompactionInputError
expected=9..9; got=9; bad_keys=0; bad_values=1; missed=0
expected=10000..10000; got=10000; bad_keys=0; bad_values=0; missed=0
==== Test CorruptionTest.CompactionInputErrorParanoid
db/corruption_test.cc:325: failed: 1 == 5
What version of the product are you using? On what operating system?
1.4, git commit "85584d497e7b354853b72f450683d59fcf6b9c5c"
OS: CentOS 5.4, kernel 2.6.35.13, x64 virtual machine(VMWare)
Please provide any additional information below.
```
-----
Original issue reported on code.google.com by `tfengjun` on 7 May 2012 at 6:21 | defect | corruption test failed db corruption test cc failed what steps will reproduce the problem make corruption test for i i do corruption test if then break fi done what is the expected output what do you see instead expected output test corruptiontest recovery expected got bad keys bad values missed expected got bad keys bad values missed test corruptiontest recoverwriteerror test corruptiontest newfileerrorduringwrite test corruptiontest tablefile expected got bad keys bad values missed test corruptiontest tablefileindexdata expected got bad keys bad values missed test corruptiontest missingdescriptor expected got bad keys bad values missed test corruptiontest sequencenumberrecovery test corruptiontest corrupteddescriptor test corruptiontest compactioninputerror expected got bad keys bad values missed expected got bad keys bad values missed test corruptiontest compactioninputerrorparanoid expected got bad keys bad values missed test corruptiontest unrelatedkeys passed tests what i see test corruptiontest recovery expected got bad keys bad values missed expected got bad keys bad values missed test corruptiontest recoverwriteerror test corruptiontest newfileerrorduringwrite test corruptiontest tablefile expected got bad keys bad values missed test corruptiontest tablefileindexdata expected got bad keys bad values missed test corruptiontest missingdescriptor expected got bad keys bad values missed test corruptiontest sequencenumberrecovery test corruptiontest corrupteddescriptor test corruptiontest compactioninputerror expected got bad keys bad values missed expected got bad keys bad values missed test corruptiontest compactioninputerrorparanoid db corruption test cc failed what version of the product are you using on what operating system git commit os centos kernel virtual machine vmware please provide any additional information below original issue reported on code google com by tfengjun on may at | 1 |
20,734 | 10,549,680,634 | IssuesEvent | 2019-10-03 09:17:15 | TIBCOSoftware/jasperreports | https://api.github.com/repos/TIBCOSoftware/jasperreports | closed | CVE-2019-14540 (High) detected in jackson-databind-2.9.9.jar | security vulnerability | ## CVE-2019-14540 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/jasperreports/jasperreports/pom.xml</p>
<p>Path to vulnerable library: epository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/TIBCOSoftware/jasperreports/commit/dddd38218a3c404d01eecdb9d9a7636fe2d02d7a">dddd38218a3c404d01eecdb9d9a7636fe2d02d7a</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariConfig.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540>CVE-2019-14540</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/blob/master/release-notes/VERSION-2.x">https://github.com/FasterXML/jackson-databind/blob/master/release-notes/VERSION-2.x</a></p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: 2.9.10</p>
</p>
</details>
<p></p>
| True | CVE-2019-14540 (High) detected in jackson-databind-2.9.9.jar - ## CVE-2019-14540 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/jasperreports/jasperreports/pom.xml</p>
<p>Path to vulnerable library: epository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/TIBCOSoftware/jasperreports/commit/dddd38218a3c404d01eecdb9d9a7636fe2d02d7a">dddd38218a3c404d01eecdb9d9a7636fe2d02d7a</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariConfig.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540>CVE-2019-14540</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/blob/master/release-notes/VERSION-2.x">https://github.com/FasterXML/jackson-databind/blob/master/release-notes/VERSION-2.x</a></p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: 2.9.10</p>
</p>
</details>
<p></p>
| non_defect | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file tmp ws scm jasperreports jasperreports pom xml path to vulnerable library epository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind before it is related to com zaxxer hikari hikariconfig publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution | 0 |
41,232 | 6,896,031,398 | IssuesEvent | 2017-11-23 16:00:09 | kinvolk/kube-spawn | https://api.github.com/repos/kinvolk/kube-spawn | closed | Document new features | documentation | - [ ] file binding/copying https://github.com/kinvolk/kube-spawn/issues/148
- [ ] multiple cluster environment workflow https://github.com/kinvolk/kube-spawn/issues/147
| 1.0 | Document new features - - [ ] file binding/copying https://github.com/kinvolk/kube-spawn/issues/148
- [ ] multiple cluster environment workflow https://github.com/kinvolk/kube-spawn/issues/147
| non_defect | document new features file binding copying multiple cluster environment workflow | 0 |
225,674 | 17,274,019,799 | IssuesEvent | 2021-07-23 01:50:50 | hackforla/civic-opportunity | https://api.github.com/repos/hackforla/civic-opportunity | closed | Create First Dump of Ideas on Miro Board | documentation initiative: pilot projects role: business analyst role: data analyst | ### Overview
Brainstorm ideas to visually represent the addressable market for workforce development in LA. Then, have the team review for next steps. We want to answer questions like:
- What is the total number of unemployed people in LA?
- What is the number of unemployed people who have been in the tech industry?
- How many people are graduating from bootcamps in LA? How many people are graduating from CS programs? Design programs? etc.
- What is the total number of jobs available in LA?
### Action Items
- [x] Write down questions to answer on board
- [ ] Initial research to answer questions
- [ ] Create outline of user journey map
- [ ] Have team review for feedback
### Resources/Instructions
[Miro Board](https://miro.com/app/board/o9J_lUHfQZ8=/)
| 1.0 | Create First Dump of Ideas on Miro Board - ### Overview
Brainstorm ideas to visually represent the addressable market for workforce development in LA. Then, have the team review for next steps. We want to answer questions like:
- What is the total number of unemployed people in LA?
- What is the number of unemployed people who have been in the tech industry?
- How many people are graduating from bootcamps in LA? How many people are graduating from CS programs? Design programs? etc.
- What is the total number of jobs available in LA?
### Action Items
- [x] Write down questions to answer on board
- [ ] Initial research to answer questions
- [ ] Create outline of user journey map
- [ ] Have team review for feedback
### Resources/Instructions
[Miro Board](https://miro.com/app/board/o9J_lUHfQZ8=/)
| non_defect | create first dump of ideas on miro board overview brainstorm ideas to visually represent the addressable market for workforce development in la then have the team review for next steps we want to answer questions like what is the total number of unemployed people in la what is the number of unemployed people who have been in the tech industry how many people are graduating from bootcamps in la how many people are graduating from cs programs design programs etc what is the total number of jobs available in la action items write down questions to answer on board initial research to answer questions create outline of user journey map have team review for feedback resources instructions | 0 |
102,464 | 4,155,950,367 | IssuesEvent | 2016-06-16 16:22:43 | readium/readium-js-viewer | https://api.github.com/repos/readium/readium-js-viewer | opened | MathJax accessibility extensions integration, requires menu (currently disabled) | difficulty:Dev func:A11y func:MathML priority:Medium status:NeedMoreInfo type:Enhancement | See:
https://www.mathjax.org/mathjax-accessibility-extensions-v1-now-available
MathJax menu was removed:
https://github.com/readium/readium-js-viewer/issues/490
https://github.com/readium/readium-js/commit/9e15c7d275f74af588d1378de7108e03260d2f23
https://github.com/readium/readium-shared-js/commit/26988df4ef4f7a615b08c56ec328a2b53d53cc8a
+ @pkra | 1.0 | MathJax accessibility extensions integration, requires menu (currently disabled) - See:
https://www.mathjax.org/mathjax-accessibility-extensions-v1-now-available
MathJax menu was removed:
https://github.com/readium/readium-js-viewer/issues/490
https://github.com/readium/readium-js/commit/9e15c7d275f74af588d1378de7108e03260d2f23
https://github.com/readium/readium-shared-js/commit/26988df4ef4f7a615b08c56ec328a2b53d53cc8a
+ @pkra | non_defect | mathjax accessibility extensions integration requires menu currently disabled see mathjax menu was removed pkra | 0 |
198,416 | 22,640,453,733 | IssuesEvent | 2022-07-01 01:05:35 | dasdristanta13/streamlit-demo | https://api.github.com/repos/dasdristanta13/streamlit-demo | closed | streamlit-1.10.0-py2.py3-none-any.whl: 1 vulnerabilities (highest severity is: 4.3) - autoclosed | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>streamlit-1.10.0-py2.py3-none-any.whl</b></p></summary>
<p></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2022-29238](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29238) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.3 | notebook-6.4.12-py3-none-any.whl | Transitive | N/A | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-29238</summary>
### Vulnerable Library - <b>notebook-6.4.12-py3-none-any.whl</b></p>
<p>A web-based notebook environment for interactive computing</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/b5/62/229659241aee54be38990e06e684bcfe5c9c8727185f5e39335be8821583/notebook-6.4.12-py3-none-any.whl">https://files.pythonhosted.org/packages/b5/62/229659241aee54be38990e06e684bcfe5c9c8727185f5e39335be8821583/notebook-6.4.12-py3-none-any.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- streamlit-1.10.0-py2.py3-none-any.whl (Root Library)
- pydeck-0.7.1-py2.py3-none-any.whl
- ipywidgets-7.7.0-py2.py3-none-any.whl
- widgetsnbextension-3.6.0-py2.py3-none-any.whl
- :x: **notebook-6.4.12-py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Jupyter Notebook is a web-based notebook environment for interactive computing. Prior to version 6.4.12, authenticated requests to the notebook server with `ContentsManager.allow_hidden = False` only prevented listing the contents of hidden directories, not accessing individual hidden files or files in hidden directories (i.e. hidden files were 'hidden' but not 'inaccessible'). This could lead to notebook configurations allowing authenticated access to files that may reasonably be expected to be disallowed. Because fully authenticated requests are required, this is of relatively low impact. But if a server's root directory contains sensitive files whose only protection from the server is being hidden (e.g. `~/.ssh` while serving $HOME), then any authenticated requests could access files if their names are guessable. Such contexts also necessarily have full access to the server and therefore execution permissions, which also generally grants access to all the same files. So this does not generally result in any privilege escalation or increase in information access, only an additional, unintended means by which the files could be accessed. Version 6.4.12 contains a patch for this issue. There are currently no known workarounds.
<p>Publish Date: 2022-06-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29238>CVE-2022-29238</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>4.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2022-29238">https://nvd.nist.gov/vuln/detail/CVE-2022-29238</a></p>
<p>Release Date: 2022-06-14</p>
<p>Fix Resolution: notebook - 7.0.0a1;notebook - 5.7.11,5.7.7</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | True | streamlit-1.10.0-py2.py3-none-any.whl: 1 vulnerabilities (highest severity is: 4.3) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>streamlit-1.10.0-py2.py3-none-any.whl</b></p></summary>
<p></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2022-29238](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29238) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.3 | notebook-6.4.12-py3-none-any.whl | Transitive | N/A | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-29238</summary>
### Vulnerable Library - <b>notebook-6.4.12-py3-none-any.whl</b></p>
<p>A web-based notebook environment for interactive computing</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/b5/62/229659241aee54be38990e06e684bcfe5c9c8727185f5e39335be8821583/notebook-6.4.12-py3-none-any.whl">https://files.pythonhosted.org/packages/b5/62/229659241aee54be38990e06e684bcfe5c9c8727185f5e39335be8821583/notebook-6.4.12-py3-none-any.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- streamlit-1.10.0-py2.py3-none-any.whl (Root Library)
- pydeck-0.7.1-py2.py3-none-any.whl
- ipywidgets-7.7.0-py2.py3-none-any.whl
- widgetsnbextension-3.6.0-py2.py3-none-any.whl
- :x: **notebook-6.4.12-py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Jupyter Notebook is a web-based notebook environment for interactive computing. Prior to version 6.4.12, authenticated requests to the notebook server with `ContentsManager.allow_hidden = False` only prevented listing the contents of hidden directories, not accessing individual hidden files or files in hidden directories (i.e. hidden files were 'hidden' but not 'inaccessible'). This could lead to notebook configurations allowing authenticated access to files that may reasonably be expected to be disallowed. Because fully authenticated requests are required, this is of relatively low impact. But if a server's root directory contains sensitive files whose only protection from the server is being hidden (e.g. `~/.ssh` while serving $HOME), then any authenticated requests could access files if their names are guessable. Such contexts also necessarily have full access to the server and therefore execution permissions, which also generally grants access to all the same files. So this does not generally result in any privilege escalation or increase in information access, only an additional, unintended means by which the files could be accessed. Version 6.4.12 contains a patch for this issue. There are currently no known workarounds.
<p>Publish Date: 2022-06-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29238>CVE-2022-29238</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>4.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2022-29238">https://nvd.nist.gov/vuln/detail/CVE-2022-29238</a></p>
<p>Release Date: 2022-06-14</p>
<p>Fix Resolution: notebook - 7.0.0a1;notebook - 5.7.11,5.7.7</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | non_defect | streamlit none any whl vulnerabilities highest severity is autoclosed vulnerable library streamlit none any whl path to dependency file requirements txt path to vulnerable library requirements txt vulnerabilities cve severity cvss dependency type fixed in remediation available medium notebook none any whl transitive n a details cve vulnerable library notebook none any whl a web based notebook environment for interactive computing library home page a href path to dependency file requirements txt path to vulnerable library requirements txt dependency hierarchy streamlit none any whl root library pydeck none any whl ipywidgets none any whl widgetsnbextension none any whl x notebook none any whl vulnerable library found in base branch main vulnerability details jupyter notebook is a web based notebook environment for interactive computing prior to version authenticated requests to the notebook server with contentsmanager allow hidden false only prevented listing the contents of hidden directories not accessing individual hidden files or files in hidden directories i e hidden files were hidden but not inaccessible this could lead to notebook configurations allowing authenticated access to files that may reasonably be expected to be disallowed because fully authenticated requests are required this is of relatively low impact but if a server s root directory contains sensitive files whose only protection from the server is being hidden e g ssh while serving home then any authenticated requests could access files if their names are guessable such contexts also necessarily have full access to the server and therefore execution permissions which also generally grants access to all the same files so this does not generally result in any privilege escalation or increase in information access only an additional unintended means by which the files could be accessed version contains a patch for this issue there are currently no known workarounds publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution notebook notebook step up your open source security game with mend | 0 |
39,815 | 20,194,926,995 | IssuesEvent | 2022-02-11 09:47:13 | tensorflow/tensorflow | https://api.github.com/repos/tensorflow/tensorflow | opened | Tensorflow gradient tape returns exploding gradient model.trainable_variables | type:performance | Dear Tensorflow-Team,
I currently facing problems when using ```gradientTape``` facing exploding gradients. I have no problem when using tensorflows inbuild ```fit``` function. Based on the MNIST dataset my code looks the following:
```
(mnist_train, mnist_test), mnist_info = tfds.load('mnist', split=['train', 'test'], as_supervised=True, with_info=True)
def prepare(ds, batch_size=128):
ds = ds.cache()
ds = ds.batch(batch_size)
ds = ds.prefetch(tf.data.experimental.AUTOTUNE)
return ds
def split_tasks(ds, predicate):
return ds.filter(predicate), ds.filter(lambda img, label: not predicate(img, label))
task_A_train, task_B_train = split_tasks(mnist_train, lambda img, label: label % 2 == 0)
task_A_train, task_B_train = prepare(task_A_train), prepare(task_B_train)
task_A_test, task_B_test = split_tasks(mnist_test, lambda img, label: label % 2 == 0)
task_A_test, task_B_test = prepare(task_A_test), prepare(task_B_test)
def evaluate(model, test_set):
acc = tf.keras.metrics.SparseCategoricalAccuracy(name='accuracy')
for i, (imgs, labels) in enumerate(test_set):
preds = model.predict_on_batch(imgs)
acc.update_state(labels, preds)
return acc.result().numpy()
multi_task_model = tf.keras.Sequential([
tf.keras.layers.Flatten(input_shape=(28, 28, 1)),
tf.keras.layers.Dense(128, activation='relu'),
tf.keras.layers.Dense(10)
])
multi_task_model.compile(optimizer='adam', loss=sparse_categorical_crossentropy, metrics='accuracy')
def l2_penalty(model, theta_A):
penalty = 0
for i, theta_i in enumerate(model.trainable_variables):
_penalty = tf.norm(theta_i - theta_A[i])
penalty += _penalty
return 0.5*penalty
def train_with_l2(model, task_A_train, task_B_train, task_A_test, task_B_test, epochs=6):
# First we're going to fit to task A and retain a copy of parameters trained on Task A
model.fit(task_A_train, epochs=epochs)
theta_A = {n: p.value() for n, p in enumerate(model.trainable_variables.copy())}
print("Task A accuracy after training on Task A: {}".format(evaluate(model, task_A_test)))
# Metrics for the custom training loop
accuracy = tf.keras.metrics.SparseCategoricalAccuracy('accuracy')
loss = tf.keras.metrics.SparseCategoricalCrossentropy('loss')
for epoch in range(epochs):
accuracy.reset_states()
loss.reset_states()
for batch, (imgs, labels) in enumerate(task_B_train):
with tf.GradientTape() as tape:
preds = model(imgs)
# Loss is crossentropy loss with regularization term for each parameter
total_loss = model.loss(labels, preds) + l2_penalty(model, theta_A)
grads = tape.gradient(total_loss, model.trainable_variables)
model.optimizer.apply_gradients(zip(grads, model.trainable_variables))
accuracy.update_state(labels, preds)
loss.update_state(labels, preds)
print("\rEpoch: {}, Batch: {}, Loss: {:.3f}, Accuracy: {:.3f}".format(
epoch+1, batch+1, loss.result().numpy(), accuracy.result().numpy()), flush=True, end=''
)
print("")
print("Task B accuracy after training trained model on Task B: {}".format(evaluate(model, task_B_test)))
print("Task A accuracy after training trained model on Task B: {}".format(evaluate(model, task_A_test)))
```
Here are my system specifications:
- Windows
- Tensorflow installed from source (version 2.7.0)
- Python version 3.9.7
| True | Tensorflow gradient tape returns exploding gradient model.trainable_variables - Dear Tensorflow-Team,
I currently facing problems when using ```gradientTape``` facing exploding gradients. I have no problem when using tensorflows inbuild ```fit``` function. Based on the MNIST dataset my code looks the following:
```
(mnist_train, mnist_test), mnist_info = tfds.load('mnist', split=['train', 'test'], as_supervised=True, with_info=True)
def prepare(ds, batch_size=128):
ds = ds.cache()
ds = ds.batch(batch_size)
ds = ds.prefetch(tf.data.experimental.AUTOTUNE)
return ds
def split_tasks(ds, predicate):
return ds.filter(predicate), ds.filter(lambda img, label: not predicate(img, label))
task_A_train, task_B_train = split_tasks(mnist_train, lambda img, label: label % 2 == 0)
task_A_train, task_B_train = prepare(task_A_train), prepare(task_B_train)
task_A_test, task_B_test = split_tasks(mnist_test, lambda img, label: label % 2 == 0)
task_A_test, task_B_test = prepare(task_A_test), prepare(task_B_test)
def evaluate(model, test_set):
acc = tf.keras.metrics.SparseCategoricalAccuracy(name='accuracy')
for i, (imgs, labels) in enumerate(test_set):
preds = model.predict_on_batch(imgs)
acc.update_state(labels, preds)
return acc.result().numpy()
multi_task_model = tf.keras.Sequential([
tf.keras.layers.Flatten(input_shape=(28, 28, 1)),
tf.keras.layers.Dense(128, activation='relu'),
tf.keras.layers.Dense(10)
])
multi_task_model.compile(optimizer='adam', loss=sparse_categorical_crossentropy, metrics='accuracy')
def l2_penalty(model, theta_A):
penalty = 0
for i, theta_i in enumerate(model.trainable_variables):
_penalty = tf.norm(theta_i - theta_A[i])
penalty += _penalty
return 0.5*penalty
def train_with_l2(model, task_A_train, task_B_train, task_A_test, task_B_test, epochs=6):
# First we're going to fit to task A and retain a copy of parameters trained on Task A
model.fit(task_A_train, epochs=epochs)
theta_A = {n: p.value() for n, p in enumerate(model.trainable_variables.copy())}
print("Task A accuracy after training on Task A: {}".format(evaluate(model, task_A_test)))
# Metrics for the custom training loop
accuracy = tf.keras.metrics.SparseCategoricalAccuracy('accuracy')
loss = tf.keras.metrics.SparseCategoricalCrossentropy('loss')
for epoch in range(epochs):
accuracy.reset_states()
loss.reset_states()
for batch, (imgs, labels) in enumerate(task_B_train):
with tf.GradientTape() as tape:
preds = model(imgs)
# Loss is crossentropy loss with regularization term for each parameter
total_loss = model.loss(labels, preds) + l2_penalty(model, theta_A)
grads = tape.gradient(total_loss, model.trainable_variables)
model.optimizer.apply_gradients(zip(grads, model.trainable_variables))
accuracy.update_state(labels, preds)
loss.update_state(labels, preds)
print("\rEpoch: {}, Batch: {}, Loss: {:.3f}, Accuracy: {:.3f}".format(
epoch+1, batch+1, loss.result().numpy(), accuracy.result().numpy()), flush=True, end=''
)
print("")
print("Task B accuracy after training trained model on Task B: {}".format(evaluate(model, task_B_test)))
print("Task A accuracy after training trained model on Task B: {}".format(evaluate(model, task_A_test)))
```
Here are my system specifications:
- Windows
- Tensorflow installed from source (version 2.7.0)
- Python version 3.9.7
| non_defect | tensorflow gradient tape returns exploding gradient model trainable variables dear tensorflow team i currently facing problems when using gradienttape facing exploding gradients i have no problem when using tensorflows inbuild fit function based on the mnist dataset my code looks the following mnist train mnist test mnist info tfds load mnist split as supervised true with info true def prepare ds batch size ds ds cache ds ds batch batch size ds ds prefetch tf data experimental autotune return ds def split tasks ds predicate return ds filter predicate ds filter lambda img label not predicate img label task a train task b train split tasks mnist train lambda img label label task a train task b train prepare task a train prepare task b train task a test task b test split tasks mnist test lambda img label label task a test task b test prepare task a test prepare task b test def evaluate model test set acc tf keras metrics sparsecategoricalaccuracy name accuracy for i imgs labels in enumerate test set preds model predict on batch imgs acc update state labels preds return acc result numpy multi task model tf keras sequential tf keras layers flatten input shape tf keras layers dense activation relu tf keras layers dense multi task model compile optimizer adam loss sparse categorical crossentropy metrics accuracy def penalty model theta a penalty for i theta i in enumerate model trainable variables penalty tf norm theta i theta a penalty penalty return penalty def train with model task a train task b train task a test task b test epochs first we re going to fit to task a and retain a copy of parameters trained on task a model fit task a train epochs epochs theta a n p value for n p in enumerate model trainable variables copy print task a accuracy after training on task a format evaluate model task a test metrics for the custom training loop accuracy tf keras metrics sparsecategoricalaccuracy accuracy loss tf keras metrics sparsecategoricalcrossentropy loss for epoch in range epochs accuracy reset states loss reset states for batch imgs labels in enumerate task b train with tf gradienttape as tape preds model imgs loss is crossentropy loss with regularization term for each parameter total loss model loss labels preds penalty model theta a grads tape gradient total loss model trainable variables model optimizer apply gradients zip grads model trainable variables accuracy update state labels preds loss update state labels preds print repoch batch loss accuracy format epoch batch loss result numpy accuracy result numpy flush true end print print task b accuracy after training trained model on task b format evaluate model task b test print task a accuracy after training trained model on task b format evaluate model task a test here are my system specifications windows tensorflow installed from source version python version | 0 |
172,869 | 21,057,435,510 | IssuesEvent | 2022-04-01 05:50:40 | berviantoleo/SimpleBookselfAPI | https://api.github.com/repos/berviantoleo/SimpleBookselfAPI | opened | CVE-2022-21680 (High) detected in marked-2.1.3.tgz | security vulnerability | ## CVE-2022-21680 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-2.1.3.tgz</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://registry.npmjs.org/marked/-/marked-2.1.3.tgz">https://registry.npmjs.org/marked/-/marked-2.1.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/marked/package.json</p>
<p>
Dependency Hierarchy:
- typedoc-0.21.4.tgz (Root Library)
- :x: **marked-2.1.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/berviantoleo/SimpleBookselfAPI/commit/0512678749aa6f36ab12ba1c27b915b6f75fd4c7">0512678749aa6f36ab12ba1c27b915b6f75fd4c7</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Marked is a markdown parser and compiler. Prior to version 4.0.10, the regular expression `block.def` may cause catastrophic backtracking against some strings and lead to a regular expression denial of service (ReDoS). Anyone who runs untrusted markdown through a vulnerable version of marked and does not use a worker with a time limit may be affected. This issue is patched in version 4.0.10. As a workaround, avoid running untrusted markdown through marked or run marked on a worker thread and set a reasonable time limit to prevent draining resources.
<p>Publish Date: 2022-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-21680>CVE-2022-21680</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-rrrm-qjm4-v8hf">https://github.com/advisories/GHSA-rrrm-qjm4-v8hf</a></p>
<p>Release Date: 2022-01-14</p>
<p>Fix Resolution: marked - 4.0.10</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-21680 (High) detected in marked-2.1.3.tgz - ## CVE-2022-21680 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-2.1.3.tgz</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://registry.npmjs.org/marked/-/marked-2.1.3.tgz">https://registry.npmjs.org/marked/-/marked-2.1.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/marked/package.json</p>
<p>
Dependency Hierarchy:
- typedoc-0.21.4.tgz (Root Library)
- :x: **marked-2.1.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/berviantoleo/SimpleBookselfAPI/commit/0512678749aa6f36ab12ba1c27b915b6f75fd4c7">0512678749aa6f36ab12ba1c27b915b6f75fd4c7</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Marked is a markdown parser and compiler. Prior to version 4.0.10, the regular expression `block.def` may cause catastrophic backtracking against some strings and lead to a regular expression denial of service (ReDoS). Anyone who runs untrusted markdown through a vulnerable version of marked and does not use a worker with a time limit may be affected. This issue is patched in version 4.0.10. As a workaround, avoid running untrusted markdown through marked or run marked on a worker thread and set a reasonable time limit to prevent draining resources.
<p>Publish Date: 2022-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-21680>CVE-2022-21680</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-rrrm-qjm4-v8hf">https://github.com/advisories/GHSA-rrrm-qjm4-v8hf</a></p>
<p>Release Date: 2022-01-14</p>
<p>Fix Resolution: marked - 4.0.10</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_defect | cve high detected in marked tgz cve high severity vulnerability vulnerable library marked tgz a markdown parser built for speed library home page a href path to dependency file package json path to vulnerable library node modules marked package json dependency hierarchy typedoc tgz root library x marked tgz vulnerable library found in head commit a href found in base branch main vulnerability details marked is a markdown parser and compiler prior to version the regular expression block def may cause catastrophic backtracking against some strings and lead to a regular expression denial of service redos anyone who runs untrusted markdown through a vulnerable version of marked and does not use a worker with a time limit may be affected this issue is patched in version as a workaround avoid running untrusted markdown through marked or run marked on a worker thread and set a reasonable time limit to prevent draining resources publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution marked step up your open source security game with whitesource | 0 |
709,488 | 24,379,789,546 | IssuesEvent | 2022-10-04 06:41:04 | yugabyte/yugabyte-db | https://api.github.com/repos/yugabyte/yugabyte-db | closed | [YSQL] Avoid using of shared_ptr for XClusterSafeTimeMap | kind/enhancement area/ysql priority/medium status/awaiting-triage | Jira Link: [DB-3733](https://yugabyte.atlassian.net/browse/DB-3733)
### Description
`TabletServer` object is the only owner of the `XClusterSafeTimeMap` object. It is not needed to use shared_ptr | 1.0 | [YSQL] Avoid using of shared_ptr for XClusterSafeTimeMap - Jira Link: [DB-3733](https://yugabyte.atlassian.net/browse/DB-3733)
### Description
`TabletServer` object is the only owner of the `XClusterSafeTimeMap` object. It is not needed to use shared_ptr | non_defect | avoid using of shared ptr for xclustersafetimemap jira link description tabletserver object is the only owner of the xclustersafetimemap object it is not needed to use shared ptr | 0 |
213,622 | 7,255,110,496 | IssuesEvent | 2018-02-16 13:47:39 | SpamExperts/cpanel-addon | https://api.github.com/repos/SpamExperts/cpanel-addon | closed | Cpanel Addon only displays main domain instead of the full domain list | bug priority-normal | ### Version information
Controlpanel: Cpanel v11.68.0.29
PHP version: 5.6.30
Addon version: 3.0.96563
### Steps to replicate
1. Client is trying to access the domains list,however this will only list his main domain and not others added.
### Actual result
The list does not fully display
### Expected result
The client to see the full domain list
[debug.log.txt](https://github.com/SpamExperts/cpanel-addon/files/1724459/debug.log.txt)
[Cpanel issue Diagnostics page.txt](https://github.com/SpamExperts/cpanel-addon/files/1724461/Cpanel.issue.Diagnostics.page.txt)
### Other notes
https://my.spamexperts.com/admin/supporttickets.php?action=view&id=196621 | 1.0 | Cpanel Addon only displays main domain instead of the full domain list - ### Version information
Controlpanel: Cpanel v11.68.0.29
PHP version: 5.6.30
Addon version: 3.0.96563
### Steps to replicate
1. Client is trying to access the domains list,however this will only list his main domain and not others added.
### Actual result
The list does not fully display
### Expected result
The client to see the full domain list
[debug.log.txt](https://github.com/SpamExperts/cpanel-addon/files/1724459/debug.log.txt)
[Cpanel issue Diagnostics page.txt](https://github.com/SpamExperts/cpanel-addon/files/1724461/Cpanel.issue.Diagnostics.page.txt)
### Other notes
https://my.spamexperts.com/admin/supporttickets.php?action=view&id=196621 | non_defect | cpanel addon only displays main domain instead of the full domain list version information controlpanel cpanel php version addon version steps to replicate client is trying to access the domains list however this will only list his main domain and not others added actual result the list does not fully display expected result the client to see the full domain list other notes | 0 |
20,178 | 3,309,977,164 | IssuesEvent | 2015-11-05 05:30:27 | navjagpal/browser-timetracker | https://api.github.com/repos/navjagpal/browser-timetracker | closed | Can't select any options | auto-migrated Priority-Medium Type-Defect | ```
What steps will reproduce the problem?
1. Open options from tools->extensions->timetracker options
2. click checkbox
3. onClick never gets called
What is the expected output? What do you see instead?
Error in chrome devtools console states that "Refused to execute inline script
because it violates the following Content Security Policy directive:
"script-src 'self' chrome-extension-resource:"."
What version of the product are you using? On what operating system?
Chromium Version 33.0.1750.146 (254388) on Arch Linux x64
Please provide any additional information below.
There is a detailed answer for this problem (I believe) at stack overflow
http://stackoverflow.com/a/17612988/1915428
```
Original issue reported on code.google.com by `klinga.m...@gmail.com` on 9 Mar 2014 at 10:11 | 1.0 | Can't select any options - ```
What steps will reproduce the problem?
1. Open options from tools->extensions->timetracker options
2. click checkbox
3. onClick never gets called
What is the expected output? What do you see instead?
Error in chrome devtools console states that "Refused to execute inline script
because it violates the following Content Security Policy directive:
"script-src 'self' chrome-extension-resource:"."
What version of the product are you using? On what operating system?
Chromium Version 33.0.1750.146 (254388) on Arch Linux x64
Please provide any additional information below.
There is a detailed answer for this problem (I believe) at stack overflow
http://stackoverflow.com/a/17612988/1915428
```
Original issue reported on code.google.com by `klinga.m...@gmail.com` on 9 Mar 2014 at 10:11 | defect | can t select any options what steps will reproduce the problem open options from tools extensions timetracker options click checkbox onclick never gets called what is the expected output what do you see instead error in chrome devtools console states that refused to execute inline script because it violates the following content security policy directive script src self chrome extension resource what version of the product are you using on what operating system chromium version on arch linux please provide any additional information below there is a detailed answer for this problem i believe at stack overflow original issue reported on code google com by klinga m gmail com on mar at | 1 |
393,556 | 26,997,399,762 | IssuesEvent | 2023-02-10 03:04:17 | opensearch-project/reporting | https://api.github.com/repos/opensearch-project/reporting | closed | [FEATURE] Reporting CLI | documentation enhancement roadmap | ## Overview
Currently, Reporting does not have any quick out-of-box options to be able to download reports. Users have to download from OpenSearch Dashboards itself with the plugin installed. Reporting Anything provides users with a Reporting CLI to be able to download reports without requiring the use of Dashboards and the Dashboards plugin.
## Feature Suggestion
When users encounter issues using the Dashboards plugin, there is no work-around aside from a code change that can enable report downloads. Additionally, users with a specific use case for reporting will have a convenient option to download reports directly. Customers will be able to integrate this CLI component into their own workflows/environments to bypass any authentication or security issues.
User Quote - "The current manually generated csv and pdf reports are nice but it’d be great to be able to automate and send these via email or even just fetch via an API request."
## Requirements
* Provide a CLI option for downloading reports
* Enable users to set parameters
## Out of scope
* Support for scheduled reports
* Saved search reports
## Solution
### Solution overview
Reporting Anything's solution is to provide a mechanism for users to be able to download reports independent of the plugin. It will also provide extensibility in that users can create a report from anything by providing a URL, and are not limited to the report source options provided in the reporting plugin.
### Proposed Solution
The proposed solution is to provide a CLI option. Users will be able to work around authentication issues by integrating into their own workflows. For example, a user running Reporting Anything in an AWS Lambda instance will not have to deal with any security issues that they would running the Reporting plugin in OpenSearch Dashboards. From there, the user can also integrate with an email service to create an email report mechanism.
## Detailed Design
### User interface
The user interface will be on the command line, with the user being given several parameters, including:
* Saved object ID (for OpenSearch Dashboards reports)
* Report source type (Dashboard, visualization, saved search)
* Full URL of the report
* File format for download (PDF or PNG, default is PDF)
* Window width in pixels (default is 1680)
* Window height in pixels (default is 2560)
Sample commands:
```
reporting-anything --object-id 7adfa750-4c81-11e8-b3d7-01146121b73d --format pdf
```
```
reporting anything --url http://localhost:5601/app/dashboards#/view/7adfa750-4c81-11e8-b3d7-01146121b73d?_g=(filters:!(),refreshInterval:(pause:!f,value:900000),time:(from:now-24h,to:now))&_a=(description:'Analyze%20mock%20flight%20data%20for%20OpenSearch-Air,%20Logstash%20Airways,%20OpenSearch%20Dashboards%20Airlines%20and%20BeatsWest',filters:!(),fullScreenMode:!f,options:(hidePanelTitles:!f,useMargins:!t),query:(language:kuery,query:''),timeRestore:!t,title:'%5BFlights%5D%20Global%20Flight%20Dashboard',viewMode:view) --format png
```
### Component design
The only component of the project is the command line interface, which contains all the functionality for reporting anything. The design of the CLI is in the above section.
| 1.0 | [FEATURE] Reporting CLI - ## Overview
Currently, Reporting does not have any quick out-of-box options to be able to download reports. Users have to download from OpenSearch Dashboards itself with the plugin installed. Reporting Anything provides users with a Reporting CLI to be able to download reports without requiring the use of Dashboards and the Dashboards plugin.
## Feature Suggestion
When users encounter issues using the Dashboards plugin, there is no work-around aside from a code change that can enable report downloads. Additionally, users with a specific use case for reporting will have a convenient option to download reports directly. Customers will be able to integrate this CLI component into their own workflows/environments to bypass any authentication or security issues.
User Quote - "The current manually generated csv and pdf reports are nice but it’d be great to be able to automate and send these via email or even just fetch via an API request."
## Requirements
* Provide a CLI option for downloading reports
* Enable users to set parameters
## Out of scope
* Support for scheduled reports
* Saved search reports
## Solution
### Solution overview
Reporting Anything's solution is to provide a mechanism for users to be able to download reports independent of the plugin. It will also provide extensibility in that users can create a report from anything by providing a URL, and are not limited to the report source options provided in the reporting plugin.
### Proposed Solution
The proposed solution is to provide a CLI option. Users will be able to work around authentication issues by integrating into their own workflows. For example, a user running Reporting Anything in an AWS Lambda instance will not have to deal with any security issues that they would running the Reporting plugin in OpenSearch Dashboards. From there, the user can also integrate with an email service to create an email report mechanism.
## Detailed Design
### User interface
The user interface will be on the command line, with the user being given several parameters, including:
* Saved object ID (for OpenSearch Dashboards reports)
* Report source type (Dashboard, visualization, saved search)
* Full URL of the report
* File format for download (PDF or PNG, default is PDF)
* Window width in pixels (default is 1680)
* Window height in pixels (default is 2560)
Sample commands:
```
reporting-anything --object-id 7adfa750-4c81-11e8-b3d7-01146121b73d --format pdf
```
```
reporting anything --url http://localhost:5601/app/dashboards#/view/7adfa750-4c81-11e8-b3d7-01146121b73d?_g=(filters:!(),refreshInterval:(pause:!f,value:900000),time:(from:now-24h,to:now))&_a=(description:'Analyze%20mock%20flight%20data%20for%20OpenSearch-Air,%20Logstash%20Airways,%20OpenSearch%20Dashboards%20Airlines%20and%20BeatsWest',filters:!(),fullScreenMode:!f,options:(hidePanelTitles:!f,useMargins:!t),query:(language:kuery,query:''),timeRestore:!t,title:'%5BFlights%5D%20Global%20Flight%20Dashboard',viewMode:view) --format png
```
### Component design
The only component of the project is the command line interface, which contains all the functionality for reporting anything. The design of the CLI is in the above section.
| non_defect | reporting cli overview currently reporting does not have any quick out of box options to be able to download reports users have to download from opensearch dashboards itself with the plugin installed reporting anything provides users with a reporting cli to be able to download reports without requiring the use of dashboards and the dashboards plugin feature suggestion when users encounter issues using the dashboards plugin there is no work around aside from a code change that can enable report downloads additionally users with a specific use case for reporting will have a convenient option to download reports directly customers will be able to integrate this cli component into their own workflows environments to bypass any authentication or security issues user quote the current manually generated csv and pdf reports are nice but it’d be great to be able to automate and send these via email or even just fetch via an api request requirements provide a cli option for downloading reports enable users to set parameters out of scope support for scheduled reports saved search reports solution solution overview reporting anything s solution is to provide a mechanism for users to be able to download reports independent of the plugin it will also provide extensibility in that users can create a report from anything by providing a url and are not limited to the report source options provided in the reporting plugin proposed solution the proposed solution is to provide a cli option users will be able to work around authentication issues by integrating into their own workflows for example a user running reporting anything in an aws lambda instance will not have to deal with any security issues that they would running the reporting plugin in opensearch dashboards from there the user can also integrate with an email service to create an email report mechanism detailed design user interface the user interface will be on the command line with the user being given several parameters including saved object id for opensearch dashboards reports report source type dashboard visualization saved search full url of the report file format for download pdf or png default is pdf window width in pixels default is window height in pixels default is sample commands reporting anything object id format pdf reporting anything url format png component design the only component of the project is the command line interface which contains all the functionality for reporting anything the design of the cli is in the above section | 0 |
222,996 | 17,100,413,543 | IssuesEvent | 2021-07-09 10:23:48 | reptilex/tesla-style-solar-power-card | https://api.github.com/repos/reptilex/tesla-style-solar-power-card | closed | Solar values incorrect (double what they should be) w/ Tesla Powerwall | documentation | Hello, I'm using a copy-paste of the powerwall config and the solar is roughly double what is actually generated.
These pictures where taken a bit late in the day but during peak the solar was doing 7.5kw, however the card showed solar+grid backfeed power.
Here's what the card looks like:

Here's what the powerwall looks like:

and here's what HA shows for raw data
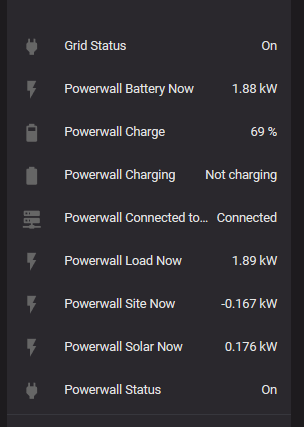
My card config is:
```
type: 'custom:tesla-style-solar-power-card'
name: Power Flow
house_entity: sensor.powerwall_load_now
grid_entity: sensor.tesla_card_grid_consumption
battery_entity: sensor.tesla_card_battery_consumption
generation_entity: sensor.powerwall_solar_now
generation_to_grid_entity: sensor.tesla_card_grid_feed_in
generation_to_house_entity: sensor.tesla_card_solar_consumption
generation_to_battery_entity: sensor.tesla_card_battery_charging
battery_to_house_entity: sensor.tesla_card_battery_consumption
grid_to_house_entity: sensor.tesla_card_grid_consumption
battery_extra_entity: sensor.powerwall_charge
hide_inactive_lines: 1
```
and the configuration.yaml is:
```
- platform: template
sensors:
tesla_card_grid_consumption:
unique_id: 'tesla_card_5fee6ddd5c1f42a099067ce9dd44e6d1'
value_template: "{{ states('sensor.powerwall_site_now') | float | max(0) }}"
device_class: power
unit_of_measurement: kW
tesla_card_grid_feed_in:
unique_id: 'tesla_card_52d22b847ade42c5b4526b2ff15f5aef'
value_template: "{{ states('sensor.powerwall_site_now') | float | min(0) | abs }}"
device_class: power
unit_of_measurement: kW
tesla_card_solar_consumption:
unique_id: 'tesla_card_2bb67bd5264f4ec39f141f1722fea085'
value_template: >-
{% set solar = states('sensor.powerwall_solar_now') | float %}
{% set house = states('sensor.powerwall_load_now') | float %}
{{ solar if house > solar else house }}
device_class: power
unit_of_measurement: kW
tesla_card_battery_consumption:
unique_id: 'tesla_card_2b7aaa2588e8480aaba586815a84fcd7'
value_template: "{{ states('sensor.powerwall_battery_now') | float | max(0) }}"
device_class: power
unit_of_measurement: kW
tesla_card_battery_charging:
unique_id: 'tesla_card_9c46447cf75942ba9ac4bcaca85ba6c5'
value_template: "{{ states('sensor.powerwall_battery_now') | float | min(0) | abs }}"
device_class: power
unit_of_measurement: kW```
| 1.0 | Solar values incorrect (double what they should be) w/ Tesla Powerwall - Hello, I'm using a copy-paste of the powerwall config and the solar is roughly double what is actually generated.
These pictures where taken a bit late in the day but during peak the solar was doing 7.5kw, however the card showed solar+grid backfeed power.
Here's what the card looks like:

Here's what the powerwall looks like:

and here's what HA shows for raw data
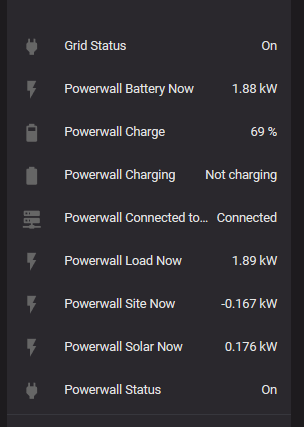
My card config is:
```
type: 'custom:tesla-style-solar-power-card'
name: Power Flow
house_entity: sensor.powerwall_load_now
grid_entity: sensor.tesla_card_grid_consumption
battery_entity: sensor.tesla_card_battery_consumption
generation_entity: sensor.powerwall_solar_now
generation_to_grid_entity: sensor.tesla_card_grid_feed_in
generation_to_house_entity: sensor.tesla_card_solar_consumption
generation_to_battery_entity: sensor.tesla_card_battery_charging
battery_to_house_entity: sensor.tesla_card_battery_consumption
grid_to_house_entity: sensor.tesla_card_grid_consumption
battery_extra_entity: sensor.powerwall_charge
hide_inactive_lines: 1
```
and the configuration.yaml is:
```
- platform: template
sensors:
tesla_card_grid_consumption:
unique_id: 'tesla_card_5fee6ddd5c1f42a099067ce9dd44e6d1'
value_template: "{{ states('sensor.powerwall_site_now') | float | max(0) }}"
device_class: power
unit_of_measurement: kW
tesla_card_grid_feed_in:
unique_id: 'tesla_card_52d22b847ade42c5b4526b2ff15f5aef'
value_template: "{{ states('sensor.powerwall_site_now') | float | min(0) | abs }}"
device_class: power
unit_of_measurement: kW
tesla_card_solar_consumption:
unique_id: 'tesla_card_2bb67bd5264f4ec39f141f1722fea085'
value_template: >-
{% set solar = states('sensor.powerwall_solar_now') | float %}
{% set house = states('sensor.powerwall_load_now') | float %}
{{ solar if house > solar else house }}
device_class: power
unit_of_measurement: kW
tesla_card_battery_consumption:
unique_id: 'tesla_card_2b7aaa2588e8480aaba586815a84fcd7'
value_template: "{{ states('sensor.powerwall_battery_now') | float | max(0) }}"
device_class: power
unit_of_measurement: kW
tesla_card_battery_charging:
unique_id: 'tesla_card_9c46447cf75942ba9ac4bcaca85ba6c5'
value_template: "{{ states('sensor.powerwall_battery_now') | float | min(0) | abs }}"
device_class: power
unit_of_measurement: kW```
| non_defect | solar values incorrect double what they should be w tesla powerwall hello i m using a copy paste of the powerwall config and the solar is roughly double what is actually generated these pictures where taken a bit late in the day but during peak the solar was doing however the card showed solar grid backfeed power here s what the card looks like here s what the powerwall looks like and here s what ha shows for raw data my card config is type custom tesla style solar power card name power flow house entity sensor powerwall load now grid entity sensor tesla card grid consumption battery entity sensor tesla card battery consumption generation entity sensor powerwall solar now generation to grid entity sensor tesla card grid feed in generation to house entity sensor tesla card solar consumption generation to battery entity sensor tesla card battery charging battery to house entity sensor tesla card battery consumption grid to house entity sensor tesla card grid consumption battery extra entity sensor powerwall charge hide inactive lines and the configuration yaml is platform template sensors tesla card grid consumption unique id tesla card value template states sensor powerwall site now float max device class power unit of measurement kw tesla card grid feed in unique id tesla card value template states sensor powerwall site now float min abs device class power unit of measurement kw tesla card solar consumption unique id tesla card value template set solar states sensor powerwall solar now float set house states sensor powerwall load now float solar if house solar else house device class power unit of measurement kw tesla card battery consumption unique id tesla card value template states sensor powerwall battery now float max device class power unit of measurement kw tesla card battery charging unique id tesla card value template states sensor powerwall battery now float min abs device class power unit of measurement kw | 0 |
233,505 | 18,991,964,062 | IssuesEvent | 2021-11-22 08:30:29 | RasaHQ/rasa | https://api.github.com/repos/RasaHQ/rasa | opened | Scheduled Model Regression Test Failed | type:bug :bug: tool:model-regression-tests | *This PR is automatically created by the Scheduled Model Regression Test workflow. Checkout the Github Action Run [here](https://github.com/RasaHQ/rasa/actions/runs/1487942302).* <br> --- <br> **Description of Problem:** <br> Scheduled Model Regression Test failed. <br> **Configuration**: `Sparse + BERT + DIET(bow) + ResponseSelector(bow)` <br> **Dataset**: `Sara` | 1.0 | Scheduled Model Regression Test Failed - *This PR is automatically created by the Scheduled Model Regression Test workflow. Checkout the Github Action Run [here](https://github.com/RasaHQ/rasa/actions/runs/1487942302).* <br> --- <br> **Description of Problem:** <br> Scheduled Model Regression Test failed. <br> **Configuration**: `Sparse + BERT + DIET(bow) + ResponseSelector(bow)` <br> **Dataset**: `Sara` | non_defect | scheduled model regression test failed this pr is automatically created by the scheduled model regression test workflow checkout the github action run description of problem scheduled model regression test failed configuration sparse bert diet bow responseselector bow dataset sara | 0 |
324,886 | 24,022,220,045 | IssuesEvent | 2022-09-15 08:36:43 | falcosecurity/plugins | https://api.github.com/repos/falcosecurity/plugins | opened | commit and release note naming conventions | kind/documentation | **What to document**
We have no definite naming conventions for either commits or release notes (I don't think we have release notes at all).
In Falco, we have a naming convention for release notes touching rulesets (see: https://github.com/falcosecurity/.github/blob/main/CONTRIBUTING.md#rule-type), but although this repository is the official place for all our plugin rulesets, we haven't something like this here.
At the same time, our changelog generation tool looks for commit messages following [conventional commits](https://www.conventionalcommits.org/en/v1.0.0/) specifications. For a given plugin, the changelog will filter commit messages in the form of `xxx(plugins): ...` or `xxx(plugins/<plugin_name>): ...`. However, there is nothing enforcing this at the CI level, not even with a warning, which ends up potentially missing valuable commits in the changelogs.
**Proposals/Idea*
- Add a CI job checking that:
- If a file changes in a `plugin/<plugin_name>` path, then the commit must follow the `xxx(plugins/<plugin_name>): ...` message pattern
- If a file changes in more than one `plugin/<plugin_name>` path, then the commit must follow the `xxx(plugins): ...` message pattern
- Check or enforce than the `rule(xxx):...` commit message format is respected, even in a looser form than what we have in Falco
| 1.0 | commit and release note naming conventions - **What to document**
We have no definite naming conventions for either commits or release notes (I don't think we have release notes at all).
In Falco, we have a naming convention for release notes touching rulesets (see: https://github.com/falcosecurity/.github/blob/main/CONTRIBUTING.md#rule-type), but although this repository is the official place for all our plugin rulesets, we haven't something like this here.
At the same time, our changelog generation tool looks for commit messages following [conventional commits](https://www.conventionalcommits.org/en/v1.0.0/) specifications. For a given plugin, the changelog will filter commit messages in the form of `xxx(plugins): ...` or `xxx(plugins/<plugin_name>): ...`. However, there is nothing enforcing this at the CI level, not even with a warning, which ends up potentially missing valuable commits in the changelogs.
**Proposals/Idea*
- Add a CI job checking that:
- If a file changes in a `plugin/<plugin_name>` path, then the commit must follow the `xxx(plugins/<plugin_name>): ...` message pattern
- If a file changes in more than one `plugin/<plugin_name>` path, then the commit must follow the `xxx(plugins): ...` message pattern
- Check or enforce than the `rule(xxx):...` commit message format is respected, even in a looser form than what we have in Falco
| non_defect | commit and release note naming conventions what to document we have no definite naming conventions for either commits or release notes i don t think we have release notes at all in falco we have a naming convention for release notes touching rulesets see but although this repository is the official place for all our plugin rulesets we haven t something like this here at the same time our changelog generation tool looks for commit messages following specifications for a given plugin the changelog will filter commit messages in the form of xxx plugins or xxx plugins however there is nothing enforcing this at the ci level not even with a warning which ends up potentially missing valuable commits in the changelogs proposals idea add a ci job checking that if a file changes in a plugin path then the commit must follow the xxx plugins message pattern if a file changes in more than one plugin path then the commit must follow the xxx plugins message pattern check or enforce than the rule xxx commit message format is respected even in a looser form than what we have in falco | 0 |
315,325 | 27,066,146,664 | IssuesEvent | 2023-02-14 00:41:52 | kubernetes/minikube | https://api.github.com/repos/kubernetes/minikube | closed | Frequent test failures of `TestFunctional/parallel/ImageCommands/ImageListJson` | priority/backlog kind/failing-test | This test has high flake rates for the following environments:
|Environment|Flake Rate (%)|
|---|---|
|[Docker_Linux_crio_arm64](https://storage.googleapis.com/minikube-flake-rate/flake_chart.html?env=Docker_Linux_crio_arm64&test=TestFunctional/parallel/ImageCommands/ImageListJson)|24.85| | 1.0 | Frequent test failures of `TestFunctional/parallel/ImageCommands/ImageListJson` - This test has high flake rates for the following environments:
|Environment|Flake Rate (%)|
|---|---|
|[Docker_Linux_crio_arm64](https://storage.googleapis.com/minikube-flake-rate/flake_chart.html?env=Docker_Linux_crio_arm64&test=TestFunctional/parallel/ImageCommands/ImageListJson)|24.85| | non_defect | frequent test failures of testfunctional parallel imagecommands imagelistjson this test has high flake rates for the following environments environment flake rate | 0 |
387,282 | 26,718,707,068 | IssuesEvent | 2023-01-28 21:36:25 | DataverseLabs/pyinterpolate | https://api.github.com/repos/DataverseLabs/pyinterpolate | closed | [Variogram] [theoretical/__init__.py] [Docstring] List of modules functions and classes, references | documentation | **Is your feature request related to a problem? Please describe.**
n/a
**Describe the solution you'd like**
- [x] list of module (`variogram.theoretical`) functions and classes,
- [x] References
**Describe alternatives you've considered**
n/a
**Additional context**
n/a
| 1.0 | [Variogram] [theoretical/__init__.py] [Docstring] List of modules functions and classes, references - **Is your feature request related to a problem? Please describe.**
n/a
**Describe the solution you'd like**
- [x] list of module (`variogram.theoretical`) functions and classes,
- [x] References
**Describe alternatives you've considered**
n/a
**Additional context**
n/a
| non_defect | list of modules functions and classes references is your feature request related to a problem please describe n a describe the solution you d like list of module variogram theoretical functions and classes references describe alternatives you ve considered n a additional context n a | 0 |
135,841 | 18,722,139,530 | IssuesEvent | 2021-11-03 13:00:21 | KDWSS/dd-trace-java | https://api.github.com/repos/KDWSS/dd-trace-java | opened | CVE-2021-22118 (High) detected in multiple libraries | security vulnerability | ## CVE-2021-22118 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>spring-web-5.3.1.jar</b>, <b>spring-web-5.2.10.RELEASE.jar</b>, <b>spring-web-5.2.6.RELEASE.jar</b>, <b>spring-web-5.3.2.jar</b>, <b>spring-web-5.2.13.RELEASE.jar</b></p></summary>
<p>
<details><summary><b>spring-web-5.3.1.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: dd-trace-java/dd-smoke-tests/spring-boot-2.4-webflux/spring-boot-2.4-webflux.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-web/5.3.1/4e1e1d1c6b5a00597162db84132414c409bcf615/spring-web-5.3.1.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-web/5.3.1/4e1e1d1c6b5a00597162db84132414c409bcf615/spring-web-5.3.1.jar</p>
<p>
Dependency Hierarchy:
- spring-webflux-5.3.1.jar (Root Library)
- :x: **spring-web-5.3.1.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-web-5.2.10.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/spring-cloud-zuul-2/spring-cloud-zuul-2.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-web/5.2.10.RELEASE/7b494eab9ea8103d79813768fe4b7e7ac6d5e4b0/spring-web-5.2.10.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.3.5.RELEASE.jar (Root Library)
- :x: **spring-web-5.2.10.RELEASE.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-web-5.2.6.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: dd-trace-java/dd-smoke-tests/springboot-openliberty/application/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-web/5.2.6.RELEASE/spring-web-5.2.6.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.2.7.RELEASE.jar (Root Library)
- :x: **spring-web-5.2.6.RELEASE.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-web-5.3.2.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: dd-trace-java/dd-smoke-tests/springboot-mongo/springboot-mongo.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-web/5.3.2/5ea6e1536ee6a70bb5c2efbd579c688c09a93a4b/spring-web-5.3.2.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.4.1.jar (Root Library)
- :x: **spring-web-5.3.2.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-web-5.2.13.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/couchbase-2.0/couchbase-2.0.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-web/5.2.13.RELEASE/346f1e07b6177cf917459d91def0dbd1a3fba172/spring-web-5.2.13.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-data-couchbase-3.2.13.RELEASE.jar (Root Library)
- :x: **spring-web-5.2.13.RELEASE.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/KDWSS/dd-trace-java/commit/2819174635979a19573ec0ce8e3e2b63a3848079">2819174635979a19573ec0ce8e3e2b63a3848079</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Spring Framework, versions 5.2.x prior to 5.2.15 and versions 5.3.x prior to 5.3.7, a WebFlux application is vulnerable to a privilege escalation: by (re)creating the temporary storage directory, a locally authenticated malicious user can read or modify files that have been uploaded to the WebFlux application, or overwrite arbitrary files with multipart request data.
<p>Publish Date: 2021-05-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-22118>CVE-2021-22118</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2021-22118">https://tanzu.vmware.com/security/cve-2021-22118</a></p>
<p>Release Date: 2021-05-27</p>
<p>Fix Resolution: org.springframework:spring-web:5.2.15,5.3.7</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"5.3.1","packageFilePaths":["/dd-smoke-tests/spring-boot-2.4-webflux/spring-boot-2.4-webflux.gradle","/dd-java-agent/instrumentation/spring-webflux-5/spring-webflux-5.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework:spring-webflux:5.3.1;org.springframework:spring-web:5.3.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.2.15,5.3.7"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"5.2.10.RELEASE","packageFilePaths":["/dd-java-agent/instrumentation/spring-cloud-zuul-2/spring-cloud-zuul-2.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.3.5.RELEASE;org.springframework:spring-web:5.2.10.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.2.15,5.3.7"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"5.2.6.RELEASE","packageFilePaths":["/dd-smoke-tests/springboot-openliberty/application/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.2.7.RELEASE;org.springframework:spring-web:5.2.6.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.2.15,5.3.7"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"5.3.2","packageFilePaths":["/dd-smoke-tests/springboot-mongo/springboot-mongo.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.4.1;org.springframework:spring-web:5.3.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.2.15,5.3.7"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"5.2.13.RELEASE","packageFilePaths":["/dd-java-agent/instrumentation/couchbase-2.0/couchbase-2.0.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.data:spring-data-couchbase:3.2.13.RELEASE;org.springframework:spring-web:5.2.13.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.2.15,5.3.7"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-22118","vulnerabilityDetails":"In Spring Framework, versions 5.2.x prior to 5.2.15 and versions 5.3.x prior to 5.3.7, a WebFlux application is vulnerable to a privilege escalation: by (re)creating the temporary storage directory, a locally authenticated malicious user can read or modify files that have been uploaded to the WebFlux application, or overwrite arbitrary files with multipart request data.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-22118","cvss3Severity":"high","cvss3Score":"7.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-22118 (High) detected in multiple libraries - ## CVE-2021-22118 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>spring-web-5.3.1.jar</b>, <b>spring-web-5.2.10.RELEASE.jar</b>, <b>spring-web-5.2.6.RELEASE.jar</b>, <b>spring-web-5.3.2.jar</b>, <b>spring-web-5.2.13.RELEASE.jar</b></p></summary>
<p>
<details><summary><b>spring-web-5.3.1.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: dd-trace-java/dd-smoke-tests/spring-boot-2.4-webflux/spring-boot-2.4-webflux.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-web/5.3.1/4e1e1d1c6b5a00597162db84132414c409bcf615/spring-web-5.3.1.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-web/5.3.1/4e1e1d1c6b5a00597162db84132414c409bcf615/spring-web-5.3.1.jar</p>
<p>
Dependency Hierarchy:
- spring-webflux-5.3.1.jar (Root Library)
- :x: **spring-web-5.3.1.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-web-5.2.10.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/spring-cloud-zuul-2/spring-cloud-zuul-2.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-web/5.2.10.RELEASE/7b494eab9ea8103d79813768fe4b7e7ac6d5e4b0/spring-web-5.2.10.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.3.5.RELEASE.jar (Root Library)
- :x: **spring-web-5.2.10.RELEASE.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-web-5.2.6.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: dd-trace-java/dd-smoke-tests/springboot-openliberty/application/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-web/5.2.6.RELEASE/spring-web-5.2.6.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.2.7.RELEASE.jar (Root Library)
- :x: **spring-web-5.2.6.RELEASE.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-web-5.3.2.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: dd-trace-java/dd-smoke-tests/springboot-mongo/springboot-mongo.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-web/5.3.2/5ea6e1536ee6a70bb5c2efbd579c688c09a93a4b/spring-web-5.3.2.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.4.1.jar (Root Library)
- :x: **spring-web-5.3.2.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-web-5.2.13.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/couchbase-2.0/couchbase-2.0.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-web/5.2.13.RELEASE/346f1e07b6177cf917459d91def0dbd1a3fba172/spring-web-5.2.13.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-data-couchbase-3.2.13.RELEASE.jar (Root Library)
- :x: **spring-web-5.2.13.RELEASE.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/KDWSS/dd-trace-java/commit/2819174635979a19573ec0ce8e3e2b63a3848079">2819174635979a19573ec0ce8e3e2b63a3848079</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Spring Framework, versions 5.2.x prior to 5.2.15 and versions 5.3.x prior to 5.3.7, a WebFlux application is vulnerable to a privilege escalation: by (re)creating the temporary storage directory, a locally authenticated malicious user can read or modify files that have been uploaded to the WebFlux application, or overwrite arbitrary files with multipart request data.
<p>Publish Date: 2021-05-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-22118>CVE-2021-22118</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2021-22118">https://tanzu.vmware.com/security/cve-2021-22118</a></p>
<p>Release Date: 2021-05-27</p>
<p>Fix Resolution: org.springframework:spring-web:5.2.15,5.3.7</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"5.3.1","packageFilePaths":["/dd-smoke-tests/spring-boot-2.4-webflux/spring-boot-2.4-webflux.gradle","/dd-java-agent/instrumentation/spring-webflux-5/spring-webflux-5.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework:spring-webflux:5.3.1;org.springframework:spring-web:5.3.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.2.15,5.3.7"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"5.2.10.RELEASE","packageFilePaths":["/dd-java-agent/instrumentation/spring-cloud-zuul-2/spring-cloud-zuul-2.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.3.5.RELEASE;org.springframework:spring-web:5.2.10.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.2.15,5.3.7"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"5.2.6.RELEASE","packageFilePaths":["/dd-smoke-tests/springboot-openliberty/application/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.2.7.RELEASE;org.springframework:spring-web:5.2.6.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.2.15,5.3.7"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"5.3.2","packageFilePaths":["/dd-smoke-tests/springboot-mongo/springboot-mongo.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.4.1;org.springframework:spring-web:5.3.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.2.15,5.3.7"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"5.2.13.RELEASE","packageFilePaths":["/dd-java-agent/instrumentation/couchbase-2.0/couchbase-2.0.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.data:spring-data-couchbase:3.2.13.RELEASE;org.springframework:spring-web:5.2.13.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.2.15,5.3.7"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-22118","vulnerabilityDetails":"In Spring Framework, versions 5.2.x prior to 5.2.15 and versions 5.3.x prior to 5.3.7, a WebFlux application is vulnerable to a privilege escalation: by (re)creating the temporary storage directory, a locally authenticated malicious user can read or modify files that have been uploaded to the WebFlux application, or overwrite arbitrary files with multipart request data.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-22118","cvss3Severity":"high","cvss3Score":"7.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"High"},"extraData":{}}</REMEDIATE> --> | non_defect | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries spring web jar spring web release jar spring web release jar spring web jar spring web release jar spring web jar spring web library home page a href path to dependency file dd trace java dd smoke tests spring boot webflux spring boot webflux gradle path to vulnerable library home wss scanner gradle caches modules files org springframework spring web spring web jar home wss scanner gradle caches modules files org springframework spring web spring web jar dependency hierarchy spring webflux jar root library x spring web jar vulnerable library spring web release jar spring web library home page a href path to dependency file dd trace java dd java agent instrumentation spring cloud zuul spring cloud zuul gradle path to vulnerable library home wss scanner gradle caches modules files org springframework spring web release spring web release jar dependency hierarchy spring boot starter web release jar root library x spring web release jar vulnerable library spring web release jar spring web library home page a href path to dependency file dd trace java dd smoke tests springboot openliberty application pom xml path to vulnerable library home wss scanner repository org springframework spring web release spring web release jar dependency hierarchy spring boot starter web release jar root library x spring web release jar vulnerable library spring web jar spring web library home page a href path to dependency file dd trace java dd smoke tests springboot mongo springboot mongo gradle path to vulnerable library home wss scanner gradle caches modules files org springframework spring web spring web jar dependency hierarchy spring boot starter web jar root library x spring web jar vulnerable library spring web release jar spring web library home page a href path to dependency file dd trace java dd java agent instrumentation couchbase couchbase gradle path to vulnerable library home wss scanner gradle caches modules files org springframework spring web release spring web release jar dependency hierarchy spring data couchbase release jar root library x spring web release jar vulnerable library found in head commit a href found in base branch master vulnerability details in spring framework versions x prior to and versions x prior to a webflux application is vulnerable to a privilege escalation by re creating the temporary storage directory a locally authenticated malicious user can read or modify files that have been uploaded to the webflux application or overwrite arbitrary files with multipart request data publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring web isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org springframework spring webflux org springframework spring web isminimumfixversionavailable true minimumfixversion org springframework spring web packagetype java groupid org springframework packagename spring web packageversion release packagefilepaths istransitivedependency true dependencytree org springframework boot spring boot starter web release org springframework spring web release isminimumfixversionavailable true minimumfixversion org springframework spring web packagetype java groupid org springframework packagename spring web packageversion release packagefilepaths istransitivedependency true dependencytree org springframework boot spring boot starter web release org springframework spring web release isminimumfixversionavailable true minimumfixversion org springframework spring web packagetype java groupid org springframework packagename spring web packageversion packagefilepaths istransitivedependency true dependencytree org springframework boot spring boot starter web org springframework spring web isminimumfixversionavailable true minimumfixversion org springframework spring web packagetype java groupid org springframework packagename spring web packageversion release packagefilepaths istransitivedependency true dependencytree org springframework data spring data couchbase release org springframework spring web release isminimumfixversionavailable true minimumfixversion org springframework spring web basebranches vulnerabilityidentifier cve vulnerabilitydetails in spring framework versions x prior to and versions x prior to a webflux application is vulnerable to a privilege escalation by re creating the temporary storage directory a locally authenticated malicious user can read or modify files that have been uploaded to the webflux application or overwrite arbitrary files with multipart request data vulnerabilityurl | 0 |
4,849 | 2,610,158,299 | IssuesEvent | 2015-02-26 18:50:14 | chrsmith/republic-at-war | https://api.github.com/repos/chrsmith/republic-at-war | closed | SFX | auto-migrated Priority-Medium Type-Defect | ```
Some audio ambient sounds not working
```
-----
Original issue reported on code.google.com by `z3r0...@gmail.com` on 30 Jan 2011 at 3:00 | 1.0 | SFX - ```
Some audio ambient sounds not working
```
-----
Original issue reported on code.google.com by `z3r0...@gmail.com` on 30 Jan 2011 at 3:00 | defect | sfx some audio ambient sounds not working original issue reported on code google com by gmail com on jan at | 1 |
70,471 | 23,184,423,695 | IssuesEvent | 2022-08-01 07:04:09 | beefproject/beef | https://api.github.com/repos/beefproject/beef | closed | Detect LastPass Not Working | Defect Module Maintainability Good First Issue Medium | #### Environment
What version/revision of BeEF are you using?
0.4.7.0-0kali7
On what version of Ruby?
1.2.5.1
On what browser?
Firefox ESR
On what operating system?
Kali
####Configuration
Are you using a non-default configuration?
No
Have you enabled or disabled any BeEF extensions?
No
####Summary
Please provide a summary of the issue.
I tried using the "Detect LastPass" command on a Windows 10 host machine to detect the LastPass extension on the Vivaldi browser but it gave me the result that LastPass was not installed
####Expected Behavior
What was the expected result?
The command would detect the LastPass extension
####Actual Behavior
What was the actual result?
The command did not detect the LastPass extension yielding a false negative
####Steps to Reproduce
Please provide steps to reproduce this issue.
1. Run beef on Kali
2. Connect to a Windows 10 zombie
3. Install Vivaldi browser and the LastPass extension on the zombie (not sure if it's exclusive to the browser)
4. Execute the "Detect LastPass" command
| 1.0 | Detect LastPass Not Working - #### Environment
What version/revision of BeEF are you using?
0.4.7.0-0kali7
On what version of Ruby?
1.2.5.1
On what browser?
Firefox ESR
On what operating system?
Kali
####Configuration
Are you using a non-default configuration?
No
Have you enabled or disabled any BeEF extensions?
No
####Summary
Please provide a summary of the issue.
I tried using the "Detect LastPass" command on a Windows 10 host machine to detect the LastPass extension on the Vivaldi browser but it gave me the result that LastPass was not installed
####Expected Behavior
What was the expected result?
The command would detect the LastPass extension
####Actual Behavior
What was the actual result?
The command did not detect the LastPass extension yielding a false negative
####Steps to Reproduce
Please provide steps to reproduce this issue.
1. Run beef on Kali
2. Connect to a Windows 10 zombie
3. Install Vivaldi browser and the LastPass extension on the zombie (not sure if it's exclusive to the browser)
4. Execute the "Detect LastPass" command
| defect | detect lastpass not working environment what version revision of beef are you using on what version of ruby on what browser firefox esr on what operating system kali configuration are you using a non default configuration no have you enabled or disabled any beef extensions no summary please provide a summary of the issue i tried using the detect lastpass command on a windows host machine to detect the lastpass extension on the vivaldi browser but it gave me the result that lastpass was not installed expected behavior what was the expected result the command would detect the lastpass extension actual behavior what was the actual result the command did not detect the lastpass extension yielding a false negative steps to reproduce please provide steps to reproduce this issue run beef on kali connect to a windows zombie install vivaldi browser and the lastpass extension on the zombie not sure if it s exclusive to the browser execute the detect lastpass command | 1 |
67,100 | 16,818,686,674 | IssuesEvent | 2021-06-17 10:25:08 | status-im/StatusQ | https://api.github.com/repos/status-im/StatusQ | opened | Extend sandbox build script to allow for qmake/qt version specification | type: build type: feature | Right now the build script simply uses `qmake` which is provided by whatever Qt version it is linked to. This makes it hard to build sandbox for different Qt versions to test upgrades etc.
Ideally, the script would rely on a global environment variable (if it exists), most likely `QT_PATH`, which should come with a `qmake` executed.
That way, switching the Qt version is as simple as updated the environment variable. This can also be done on a per command basis a la:
```
QT_PATH=path/to/qt ./scripts/build
```
In addition, there could be an accepted qt path parameter being passed to the script:
```
./scripts/build --qt-path=path/to/qt
```
The reason we need to specific an entire path and not just a version number, is because users are free to install Qt in whatever location they want, so we can't expect a particular location. | 1.0 | Extend sandbox build script to allow for qmake/qt version specification - Right now the build script simply uses `qmake` which is provided by whatever Qt version it is linked to. This makes it hard to build sandbox for different Qt versions to test upgrades etc.
Ideally, the script would rely on a global environment variable (if it exists), most likely `QT_PATH`, which should come with a `qmake` executed.
That way, switching the Qt version is as simple as updated the environment variable. This can also be done on a per command basis a la:
```
QT_PATH=path/to/qt ./scripts/build
```
In addition, there could be an accepted qt path parameter being passed to the script:
```
./scripts/build --qt-path=path/to/qt
```
The reason we need to specific an entire path and not just a version number, is because users are free to install Qt in whatever location they want, so we can't expect a particular location. | non_defect | extend sandbox build script to allow for qmake qt version specification right now the build script simply uses qmake which is provided by whatever qt version it is linked to this makes it hard to build sandbox for different qt versions to test upgrades etc ideally the script would rely on a global environment variable if it exists most likely qt path which should come with a qmake executed that way switching the qt version is as simple as updated the environment variable this can also be done on a per command basis a la qt path path to qt scripts build in addition there could be an accepted qt path parameter being passed to the script scripts build qt path path to qt the reason we need to specific an entire path and not just a version number is because users are free to install qt in whatever location they want so we can t expect a particular location | 0 |
45,804 | 13,055,750,950 | IssuesEvent | 2020-07-30 02:37:38 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | opened | python scripts can become detached from terminals and eat CPU in the background (Trac #75) | IceTray Incomplete Migration Migrated from Trac defect | Migrated from https://code.icecube.wisc.edu/ticket/75
```json
{
"status": "closed",
"changetime": "2007-11-11T03:17:44",
"description": "possibly this is root's signal interference again. we may want to do something about this once and for all.\n ",
"reporter": "troy",
"cc": "",
"resolution": "duplicate",
"_ts": "1194751064000000",
"component": "IceTray",
"summary": "python scripts can become detached from terminals and eat CPU in the background",
"priority": "normal",
"keywords": "",
"time": "2007-07-02T19:33:51",
"milestone": "",
"owner": "troy",
"type": "defect"
}
```
| 1.0 | python scripts can become detached from terminals and eat CPU in the background (Trac #75) - Migrated from https://code.icecube.wisc.edu/ticket/75
```json
{
"status": "closed",
"changetime": "2007-11-11T03:17:44",
"description": "possibly this is root's signal interference again. we may want to do something about this once and for all.\n ",
"reporter": "troy",
"cc": "",
"resolution": "duplicate",
"_ts": "1194751064000000",
"component": "IceTray",
"summary": "python scripts can become detached from terminals and eat CPU in the background",
"priority": "normal",
"keywords": "",
"time": "2007-07-02T19:33:51",
"milestone": "",
"owner": "troy",
"type": "defect"
}
```
| defect | python scripts can become detached from terminals and eat cpu in the background trac migrated from json status closed changetime description possibly this is root s signal interference again we may want to do something about this once and for all n reporter troy cc resolution duplicate ts component icetray summary python scripts can become detached from terminals and eat cpu in the background priority normal keywords time milestone owner troy type defect | 1 |
163,497 | 6,199,480,478 | IssuesEvent | 2017-07-05 21:41:41 | fedarko/MetagenomeScope | https://api.github.com/repos/fedarko/MetagenomeScope | opened | Add color specification option to viewer interface | highpriorityfeature | - Extreme colors in node colorization (two main options here, right?)
- "High" outlier and "low" outlier colors in edge scaling
- Colors of "standard" node groups (bubbles, frayed ropes, chains, cyclic chains), SPQR tree metanodes (S, P, R), and maybe bicomponent "nodes"
- Unselected and selected noncolorized node colors
- Exposing this as a configurable feature would necessitate using a specific node "selected" color instead of just using the `background-blacken` feature for selected nodes, and that doesn't work well with continuous node colorizations -- maybe just don't expose the "selected node" color option?
- Unselected and selected edge colors
- | 1.0 | Add color specification option to viewer interface - - Extreme colors in node colorization (two main options here, right?)
- "High" outlier and "low" outlier colors in edge scaling
- Colors of "standard" node groups (bubbles, frayed ropes, chains, cyclic chains), SPQR tree metanodes (S, P, R), and maybe bicomponent "nodes"
- Unselected and selected noncolorized node colors
- Exposing this as a configurable feature would necessitate using a specific node "selected" color instead of just using the `background-blacken` feature for selected nodes, and that doesn't work well with continuous node colorizations -- maybe just don't expose the "selected node" color option?
- Unselected and selected edge colors
- | non_defect | add color specification option to viewer interface extreme colors in node colorization two main options here right high outlier and low outlier colors in edge scaling colors of standard node groups bubbles frayed ropes chains cyclic chains spqr tree metanodes s p r and maybe bicomponent nodes unselected and selected noncolorized node colors exposing this as a configurable feature would necessitate using a specific node selected color instead of just using the background blacken feature for selected nodes and that doesn t work well with continuous node colorizations maybe just don t expose the selected node color option unselected and selected edge colors | 0 |
52,010 | 13,211,359,925 | IssuesEvent | 2020-08-15 22:34:11 | icecube-trac/tix4 | https://api.github.com/repos/icecube-trac/tix4 | opened | [muongun] cubature memory leaks (Trac #1471) | Incomplete Migration Migrated from Trac combo simulation defect | <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/1471">https://code.icecube.wisc.edu/projects/icecube/ticket/1471</a>, reported by david.schultzand owned by jvansanten</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2016-03-18T21:14:10",
"_ts": "1458335650323600",
"description": "cubature.c\n\nline 1015:\nhttp://software.icecube.wisc.edu/static_analysis/2015-12-07-030322-70644-1/report-eb2bb2.html#EndPath\n\nAlso, line 969 (the realloc) looks fishy. If it fails it will return a NULL pointer, but the previous pointer is still valid memory that should be deallocated. This code seems to let that previous memory leak when it overwrites the pointer address.",
"reporter": "david.schultz",
"cc": "olivas",
"resolution": "fixed",
"time": "2015-12-07T22:35:06",
"component": "combo simulation",
"summary": "[muongun] cubature memory leaks",
"priority": "critical",
"keywords": "",
"milestone": "",
"owner": "jvansanten",
"type": "defect"
}
```
</p>
</details>
| 1.0 | [muongun] cubature memory leaks (Trac #1471) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/1471">https://code.icecube.wisc.edu/projects/icecube/ticket/1471</a>, reported by david.schultzand owned by jvansanten</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2016-03-18T21:14:10",
"_ts": "1458335650323600",
"description": "cubature.c\n\nline 1015:\nhttp://software.icecube.wisc.edu/static_analysis/2015-12-07-030322-70644-1/report-eb2bb2.html#EndPath\n\nAlso, line 969 (the realloc) looks fishy. If it fails it will return a NULL pointer, but the previous pointer is still valid memory that should be deallocated. This code seems to let that previous memory leak when it overwrites the pointer address.",
"reporter": "david.schultz",
"cc": "olivas",
"resolution": "fixed",
"time": "2015-12-07T22:35:06",
"component": "combo simulation",
"summary": "[muongun] cubature memory leaks",
"priority": "critical",
"keywords": "",
"milestone": "",
"owner": "jvansanten",
"type": "defect"
}
```
</p>
</details>
| defect | cubature memory leaks trac migrated from json status closed changetime ts description cubature c n nline n line the realloc looks fishy if it fails it will return a null pointer but the previous pointer is still valid memory that should be deallocated this code seems to let that previous memory leak when it overwrites the pointer address reporter david schultz cc olivas resolution fixed time component combo simulation summary cubature memory leaks priority critical keywords milestone owner jvansanten type defect | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.