Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 757 | labels stringlengths 4 664 | body stringlengths 3 261k | index stringclasses 10
values | text_combine stringlengths 96 261k | label stringclasses 2
values | text stringlengths 96 232k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
63,425 | 17,646,874,921 | IssuesEvent | 2021-08-20 07:38:01 | unascribed/Fabrication | https://api.github.com/repos/unascribed/Fabrication | opened | Exploding newlines on Windows | k: Defect | In some cases, Fabrication rewriting one of its own INI files can result in every newline being duplicated on Windows, causing the file to become s p r e a d o u t over time.
This likely has to do with Windows `\r\n` newlines, and as such can likely be reproduced on a Linux system using `unix2dos`. | 1.0 | Exploding newlines on Windows - In some cases, Fabrication rewriting one of its own INI files can result in every newline being duplicated on Windows, causing the file to become s p r e a d o u t over time.
This likely has to do with Windows `\r\n` newlines, and as such can likely be reproduced on a Linux system... | defect | exploding newlines on windows in some cases fabrication rewriting one of its own ini files can result in every newline being duplicated on windows causing the file to become s p r e a d o u t over time this likely has to do with windows r n newlines and as such can likely be reproduced on a linux system... | 1 |
60,224 | 14,531,605,541 | IssuesEvent | 2020-12-14 21:03:17 | hydrogen-dev/SDK | https://api.github.com/repos/hydrogen-dev/SDK | opened | CVE-2020-15250 (Medium) detected in junit-4.12.jar | security vulnerability | ## CVE-2020-15250 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>junit-4.12.jar</b></p></summary>
<p>JUnit is a unit testing framework for Java, created by Erich Gamma and Kent Beck... | True | CVE-2020-15250 (Medium) detected in junit-4.12.jar - ## CVE-2020-15250 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>junit-4.12.jar</b></p></summary>
<p>JUnit is a unit testing fra... | non_defect | cve medium detected in junit jar cve medium severity vulnerability vulnerable library junit jar junit is a unit testing framework for java created by erich gamma and kent beck library home page a href path to dependency file sdk atom nucleus java build gradle path to vu... | 0 |
50,089 | 13,187,322,670 | IssuesEvent | 2020-08-13 03:02:48 | icecube-trac/tix3 | https://api.github.com/repos/icecube-trac/tix3 | closed | can't modify CMAKE_INSTALL_PREFIX in cache (Trac #105) | Migrated from Trac cmake defect | for instance, if your svn doesn't support --xml.
also make tarball w/o svn revision/metaproject should probably remind
that your svn is old as dog.
<details>
<summary>_Migrated from https://code.icecube.wisc.edu/ticket/105
, reported by troy and owned by troy_</summary>
<p>
```json
{
"status": "closed",
... | 1.0 | can't modify CMAKE_INSTALL_PREFIX in cache (Trac #105) - for instance, if your svn doesn't support --xml.
also make tarball w/o svn revision/metaproject should probably remind
that your svn is old as dog.
<details>
<summary>_Migrated from https://code.icecube.wisc.edu/ticket/105
, reported by troy and owned by tr... | defect | can t modify cmake install prefix in cache trac for instance if your svn doesn t support xml also make tarball w o svn revision metaproject should probably remind that your svn is old as dog migrated from reported by troy and owned by troy json status closed changetim... | 1 |
46,585 | 13,055,940,575 | IssuesEvent | 2020-07-30 03:10:58 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | opened | new release of icerec.IC2012-L3_Cascade (Trac #1509) | Incomplete Migration Migrated from Trac combo reconstruction defect | Migrated from https://code.icecube.wisc.edu/ticket/1509
```json
{
"status": "closed",
"changetime": "2016-03-18T21:14:15",
"description": "Need an updated version of IC2012-L3_Cascade for compatibility:\n\n{{{\nRuntimeError: Attempting to read version 2 from file but running version 1 of OMKey class. (in ... | 1.0 | new release of icerec.IC2012-L3_Cascade (Trac #1509) - Migrated from https://code.icecube.wisc.edu/ticket/1509
```json
{
"status": "closed",
"changetime": "2016-03-18T21:14:15",
"description": "Need an updated version of IC2012-L3_Cascade for compatibility:\n\n{{{\nRuntimeError: Attempting to read version... | defect | new release of icerec cascade trac migrated from json status closed changetime description need an updated version of cascade for compatibility n n nruntimeerror attempting to read version from file but running version of omkey class in void omkey... | 1 |
52,037 | 12,842,181,492 | IssuesEvent | 2020-07-08 01:18:54 | mapbox/mapbox-navigation-ios | https://api.github.com/repos/mapbox/mapbox-navigation-ios | closed | CarPlay example application crashes on launch — OHHTTPStubs not found | - build CarPlay | The CarPlay example application crashes on launch because of https://github.com/mapbox/mapbox-navigation-ios/pull/2405#discussion_r441197749:
```
dyld: Library not loaded: @rpath/OHHTTPStubs.framework/OHHTTPStubs
Referenced from: /path/to/Library/Developer/CoreSimulator/Devices/8CA16171-52BF-47D5-BC13-E534EA485D... | 1.0 | CarPlay example application crashes on launch — OHHTTPStubs not found - The CarPlay example application crashes on launch because of https://github.com/mapbox/mapbox-navigation-ios/pull/2405#discussion_r441197749:
```
dyld: Library not loaded: @rpath/OHHTTPStubs.framework/OHHTTPStubs
Referenced from: /path/to/Li... | non_defect | carplay example application crashes on launch — ohhttpstubs not found the carplay example application crashes on launch because of dyld library not loaded rpath ohhttpstubs framework ohhttpstubs referenced from path to library developer coresimulator devices data containers bundle applicat... | 0 |
78,926 | 27,823,582,707 | IssuesEvent | 2023-03-19 14:12:15 | cakephp/bake | https://api.github.com/repos/cakephp/bake | closed | Column with *_id not generating a `belongsTo` relation anymore. | defect | ### Description
I guess this is a feature which was introduced recently. So if you e.g. have a table `articles` and a field `image_id`, the generated `ArticlesTable` no longer has a relation to `Images`, if there is not actually an `images` table in the database.
This "bug" was practical for my assets plugin which... | 1.0 | Column with *_id not generating a `belongsTo` relation anymore. - ### Description
I guess this is a feature which was introduced recently. So if you e.g. have a table `articles` and a field `image_id`, the generated `ArticlesTable` no longer has a relation to `Images`, if there is not actually an `images` table in the... | defect | column with id not generating a belongsto relation anymore description i guess this is a feature which was introduced recently so if you e g have a table articles and a field image id the generated articlestable no longer has a relation to images if there is not actually an images table in the... | 1 |
5,545 | 2,610,189,653 | IssuesEvent | 2015-02-26 19:00:04 | chrsmith/quchuseban | https://api.github.com/repos/chrsmith/quchuseban | opened | 关注脸上的色斑怎样去除 | auto-migrated Priority-Medium Type-Defect | ```
《摘要》
踏着风的节奏,辗转于渺渺人生驿站,看人来人往、车水马��
�随风绝尘。匆匆的步伐,试图一点一滴叩开炫目峻冷世界的�
��壳。风起风落,花开花谢,梦想的心灯明明灭灭,举目所及
,仍是不曾相识的茫然。秋风乍起,倦怠许久的灵魂,再次��
�放逐在流浪的旅途。流浪因为不想寂寞,可是没有你的日子�
��怎么办,如果没有了色斑,你还会回来吗!脸上的色斑怎样
去除,
《客户案例》
色斑,也就是隐藏哎皮肤里面的一点黑色素,但是去除��
�斑可真不是件容易的事,我的祛斑之路走得可真辛苦。<br>
大家都知道,脸是女人展示自我风采与形象魅力的门户��
�是女人骄傲的资本。但是,如果一张白皙鲜亮,光彩照人的�
��满色斑,那么,... | 1.0 | 关注脸上的色斑怎样去除 - ```
《摘要》
踏着风的节奏,辗转于渺渺人生驿站,看人来人往、车水马��
�随风绝尘。匆匆的步伐,试图一点一滴叩开炫目峻冷世界的�
��壳。风起风落,花开花谢,梦想的心灯明明灭灭,举目所及
,仍是不曾相识的茫然。秋风乍起,倦怠许久的灵魂,再次��
�放逐在流浪的旅途。流浪因为不想寂寞,可是没有你的日子�
��怎么办,如果没有了色斑,你还会回来吗!脸上的色斑怎样
去除,
《客户案例》
色斑,也就是隐藏哎皮肤里面的一点黑色素,但是去除��
�斑可真不是件容易的事,我的祛斑之路走得可真辛苦。<br>
大家都知道,脸是女人展示自我风采与形象魅力的门户��
�是女人骄傲的资本。但是,如果一张白皙鲜亮,光... | defect | 关注脸上的色斑怎样去除 《摘要》 踏着风的节奏,辗转于渺渺人生驿站,看人来人往、车水马�� �随风绝尘。匆匆的步伐,试图一点一滴叩开炫目峻冷世界的� ��壳。风起风落,花开花谢,梦想的心灯明明灭灭,举目所及 ,仍是不曾相识的茫然。秋风乍起,倦怠许久的灵魂,再次�� �放逐在流浪的旅途。流浪因为不想寂寞,可是没有你的日子� ��怎么办,如果没有了色斑,你还会回来吗!脸上的色斑怎样 去除, 《客户案例》 色斑,也就是隐藏哎皮肤里面的一点黑色素,但是去除�� �斑可真不是件容易的事,我的祛斑之路走得可真辛苦。 大家都知道,脸是女人展示自我风采与形象魅力的门户�� �是女人骄傲的资本。但是,如果一张白皙鲜亮,光彩照人... | 1 |
21,423 | 3,507,146,612 | IssuesEvent | 2016-01-08 11:31:08 | scipy/scipy | https://api.github.com/repos/scipy/scipy | closed | scipy.stats.ttest_ind_from_stats does not accept arrays | defect easy-fix scipy.stats | the use of float in the denominator prevents using arrays
Reproduce via:
```
In [158]: import scipy
In [159]: scipy.__version__
Out[159]: '0.16.1'
In [160]: from scipy.stats import ttest_ind_from_stats
In [161]: ttest_ind_from_stats(np.array([1., 2.]), np.array([.5, .3]), np.array([130, 140]), np.array(... | 1.0 | scipy.stats.ttest_ind_from_stats does not accept arrays - the use of float in the denominator prevents using arrays
Reproduce via:
```
In [158]: import scipy
In [159]: scipy.__version__
Out[159]: '0.16.1'
In [160]: from scipy.stats import ttest_ind_from_stats
In [161]: ttest_ind_from_stats(np.array([1.,... | defect | scipy stats ttest ind from stats does not accept arrays the use of float in the denominator prevents using arrays reproduce via in import scipy in scipy version out in from scipy stats import ttest ind from stats in ttest ind from stats np array np array np array... | 1 |
76,251 | 26,332,417,429 | IssuesEvent | 2023-01-10 11:52:16 | jOOQ/jOOQ | https://api.github.com/repos/jOOQ/jOOQ | closed | Support parsing ALL keyword in aggregate functions | T: Defect P: Medium R: Fixed E: All Editions C: Parser | This is valid in Db2 (and probably others, since its standard SQL):
```sql
select listagg(all 1) within group (order by 2)
from sysibm.dual
```
But our parser rejects it:
```
Token ')' expected: [1:20] select listagg(all [*]1) within group (order by 2)
from sysibm.dual
```
Other aggregate functions al... | 1.0 | Support parsing ALL keyword in aggregate functions - This is valid in Db2 (and probably others, since its standard SQL):
```sql
select listagg(all 1) within group (order by 2)
from sysibm.dual
```
But our parser rejects it:
```
Token ')' expected: [1:20] select listagg(all [*]1) within group (order by 2)
... | defect | support parsing all keyword in aggregate functions this is valid in and probably others since its standard sql sql select listagg all within group order by from sysibm dual but our parser rejects it token expected select listagg all within group order by from sysi... | 1 |
30,614 | 6,193,972,551 | IssuesEvent | 2017-07-05 08:45:20 | contao/core-bundle | https://api.github.com/repos/contao/core-bundle | closed | Layout looks weird on the maintenance page in 4.4.0 | defect | When the window (or screen) is higher than the content on the maintenance page, the 'Purge data' section is sticked at the bottom and there is a gap to the 'Rebuild the search index' section:
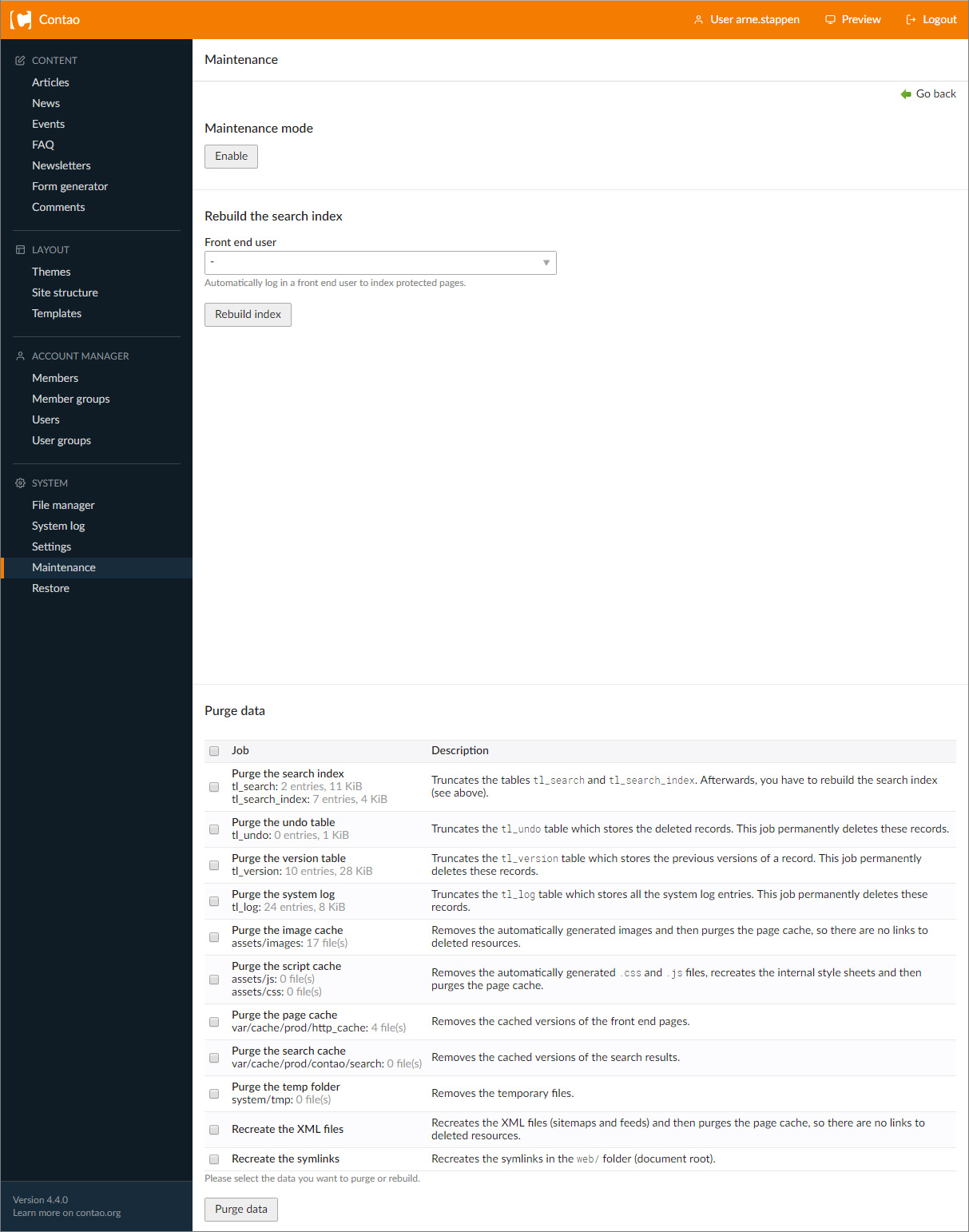
Anot... | 1.0 | Layout looks weird on the maintenance page in 4.4.0 - When the window (or screen) is higher than the content on the maintenance page, the 'Purge data' section is sticked at the bottom and there is a gap to the 'Rebuild the search index' section:
 detected in mocha-2.5.3.tgz | security vulnerability | ## WS-2021-0638 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mocha-2.5.3.tgz</b></p></summary>
<p>simple, flexible, fun test framework</p>
<p>Library home page: <a href="https://reg... | True | WS-2021-0638 (High) detected in mocha-2.5.3.tgz - ## WS-2021-0638 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mocha-2.5.3.tgz</b></p></summary>
<p>simple, flexible, fun test framew... | non_defect | ws high detected in mocha tgz ws high severity vulnerability vulnerable library mocha tgz simple flexible fun test framework library home page a href path to dependency file package json path to vulnerable library node modules mocha package json dependency hi... | 0 |
274,611 | 8,563,386,967 | IssuesEvent | 2018-11-09 13:54:09 | The-Barrens-org/Bugtracker | https://api.github.com/repos/The-Barrens-org/Bugtracker | closed | nightfin snappers not being fished at night | Item Priority - Mid Status - Fixed on Live Server | **Current behaviour:**
Nightfin snappers are not available to be fished at night (Midnight - 6am Server time). They are fishable during the day at ~10% of all catches. Tested in Moonglade and Felwood.
**Expected behaviour:**
Nightfin snappers should caught at higher frequently during night time.
**Steps to rep... | 1.0 | nightfin snappers not being fished at night - **Current behaviour:**
Nightfin snappers are not available to be fished at night (Midnight - 6am Server time). They are fishable during the day at ~10% of all catches. Tested in Moonglade and Felwood.
**Expected behaviour:**
Nightfin snappers should caught at higher f... | non_defect | nightfin snappers not being fished at night current behaviour nightfin snappers are not available to be fished at night midnight server time they are fishable during the day at of all catches tested in moonglade and felwood expected behaviour nightfin snappers should caught at higher freq... | 0 |
89,064 | 10,587,480,310 | IssuesEvent | 2019-10-08 22:16:38 | operator-framework/operator-sdk | https://api.github.com/repos/operator-framework/operator-sdk | closed | Consider adding [type] before 'User Guide' on docs user-guides | kind/documentation | ## Feature Request
Currently when you search for terms like 'Ansible Operator SDK' or 'Helm Operator SDK' (or anything of the like), you usually end up hitting proposal docs or other less relevant example documentation... you never see the "User Guide" for these items.
The reason is all these documents have the p... | 1.0 | Consider adding [type] before 'User Guide' on docs user-guides - ## Feature Request
Currently when you search for terms like 'Ansible Operator SDK' or 'Helm Operator SDK' (or anything of the like), you usually end up hitting proposal docs or other less relevant example documentation... you never see the "User Guide"... | non_defect | consider adding before user guide on docs user guides feature request currently when you search for terms like ansible operator sdk or helm operator sdk or anything of the like you usually end up hitting proposal docs or other less relevant example documentation you never see the user guide for ... | 0 |
81,489 | 10,239,496,493 | IssuesEvent | 2019-08-19 18:23:43 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | Document minimum roles required to a service principal | [zube]: To Test area/aks area/documentation kind/task team/az | I checked the scenarios in rancher/rancher#11492 and I am doing the first option, adding the cluster that already exists. The cluster was created with the service principal, which I also use in the Rancher form to add a new cluster.
Authentication test completes and I enter the existing resource group. When I get to t... | 1.0 | Document minimum roles required to a service principal - I checked the scenarios in rancher/rancher#11492 and I am doing the first option, adding the cluster that already exists. The cluster was created with the service principal, which I also use in the Rancher form to add a new cluster.
Authentication test completes... | non_defect | document minimum roles required to a service principal i checked the scenarios in rancher rancher and i am doing the first option adding the cluster that already exists the cluster was created with the service principal which i also use in the rancher form to add a new cluster authentication test completes and... | 0 |
97,529 | 16,236,387,710 | IssuesEvent | 2021-05-07 01:37:01 | rvvergara/post_and_comment_app | https://api.github.com/repos/rvvergara/post_and_comment_app | opened | CVE-2020-15169 (Medium) detected in actionview-5.2.1.gem | security vulnerability | ## CVE-2020-15169 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>actionview-5.2.1.gem</b></p></summary>
<p>Simple, battle-tested conventions and helpers for building web pages.</p>
... | True | CVE-2020-15169 (Medium) detected in actionview-5.2.1.gem - ## CVE-2020-15169 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>actionview-5.2.1.gem</b></p></summary>
<p>Simple, battle-... | non_defect | cve medium detected in actionview gem cve medium severity vulnerability vulnerable library actionview gem simple battle tested conventions and helpers for building web pages library home page a href dependency hierarchy sass rails gem root library ... | 0 |
609,462 | 18,873,889,662 | IssuesEvent | 2021-11-13 17:27:16 | praveenpal12345/Project-Practice-Lab | https://api.github.com/repos/praveenpal12345/Project-Practice-Lab | opened | Search field is case sensitive in Order section at POS User Front end | bug low priority High severity | Commit Id:
Video: https://nimb.ws/XSUGiN
----------------Steps to reproduce-----------
1. login with valid username and Password at POS end.(username peterdoe)
2. click on order section.
3. enter the customer name in search field in lowercase(like 'kate').
Expected Result : It should show order list of p... | 1.0 | Search field is case sensitive in Order section at POS User Front end - Commit Id:
Video: https://nimb.ws/XSUGiN
----------------Steps to reproduce-----------
1. login with valid username and Password at POS end.(username peterdoe)
2. click on order section.
3. enter the customer name in search field in low... | non_defect | search field is case sensitive in order section at pos user front end commit id video steps to reproduce login with valid username and password at pos end username peterdoe click on order section enter the customer name in search field in lowercase like kate ... | 0 |
32,741 | 6,911,668,548 | IssuesEvent | 2017-11-28 09:15:23 | primefaces/primereact | https://api.github.com/repos/primefaces/primereact | closed | Datatable - not propagate prop filterMatchMode when lazyload is on | defect | When you configure a DataTable to work with lazyLoad, and a Column with property filterMatchMode, this property will not propagate to onload event. It's necessary do that to make sure the backend will be correct configured. | 1.0 | Datatable - not propagate prop filterMatchMode when lazyload is on - When you configure a DataTable to work with lazyLoad, and a Column with property filterMatchMode, this property will not propagate to onload event. It's necessary do that to make sure the backend will be correct configured. | defect | datatable not propagate prop filtermatchmode when lazyload is on when you configure a datatable to work with lazyload and a column with property filtermatchmode this property will not propagate to onload event it s necessary do that to make sure the backend will be correct configured | 1 |
49,056 | 13,438,236,304 | IssuesEvent | 2020-09-07 17:34:14 | AOSC-Dev/aosc-os-abbs | https://api.github.com/repos/AOSC-Dev/aosc-os-abbs | closed | ntp: security update to 4.2.8p15 | security to-stable upgrade | <!-- Please remove items do not apply. -->
**CVE IDs:** CVE-2020-11868, CVE-2020-13817, CVE-2020-15025
**Other security advisory IDs:** openSUSE-SU-2020:1007-1
**Description:**
- CVE-2020-11868: Fixed an issue which a server mode packet with spoofed
source address frequently send to the client ntpd c... | True | ntp: security update to 4.2.8p15 - <!-- Please remove items do not apply. -->
**CVE IDs:** CVE-2020-11868, CVE-2020-13817, CVE-2020-15025
**Other security advisory IDs:** openSUSE-SU-2020:1007-1
**Description:**
- CVE-2020-11868: Fixed an issue which a server mode packet with spoofed
source address f... | non_defect | ntp security update to cve ids cve cve cve other security advisory ids opensuse su description cve fixed an issue which a server mode packet with spoofed source address frequently send to the client ntpd could have caused denial of service b... | 0 |
250,753 | 27,111,300,091 | IssuesEvent | 2023-02-15 15:29:23 | EliyaC/NodeGoat | https://api.github.com/repos/EliyaC/NodeGoat | closed | CVE-2022-29244 (High) detected in npm-3.10.10.tgz - autoclosed | security vulnerability | ## CVE-2022-29244 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>npm-3.10.10.tgz</b></p></summary>
<p>a package manager for JavaScript</p>
<p>Library home page: <a href="https://regis... | True | CVE-2022-29244 (High) detected in npm-3.10.10.tgz - autoclosed - ## CVE-2022-29244 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>npm-3.10.10.tgz</b></p></summary>
<p>a package manage... | non_defect | cve high detected in npm tgz autoclosed cve high severity vulnerability vulnerable library npm tgz a package manager for javascript library home page a href path to dependency file package json path to vulnerable library node modules npm package json dependen... | 0 |
66,460 | 20,201,964,008 | IssuesEvent | 2022-02-11 16:05:49 | department-of-veterans-affairs/va.gov-cms | https://api.github.com/repos/department-of-veterans-affairs/va.gov-cms | closed | Content releases fail with "AMI <id...> is pending, and cannot be run" | Defect Unplanned work Platform CMS Team | ## Describe the defect
Late in the day on 02/10, content releases started failing with errors like the folllowing:
<img width="749" alt="Screen Shot 2022-02-10 at 5 51 20 PM" src="https://user-images.githubusercontent.com/1318579/153625531-e7f9e4c9-1f7e-4e4f-8c5c-6988a79f419c.png">
This ended up being a result o... | 1.0 | Content releases fail with "AMI <id...> is pending, and cannot be run" - ## Describe the defect
Late in the day on 02/10, content releases started failing with errors like the folllowing:
<img width="749" alt="Screen Shot 2022-02-10 at 5 51 20 PM" src="https://user-images.githubusercontent.com/1318579/153625531-e7f... | defect | content releases fail with ami is pending and cannot be run describe the defect late in the day on content releases started failing with errors like the folllowing img width alt screen shot at pm src this ended up being a result of incorrect syntax in the content release git... | 1 |
736,938 | 25,493,405,619 | IssuesEvent | 2022-11-27 11:24:58 | fredo-ai/Fredo-Public | https://api.github.com/repos/fredo-ai/Fredo-Public | closed | Default fallback flow | priority-1 | 1. create a new template for the fallback message: https://miro.com/app/board/o9J_lttkfEA=/?moveToWidget=3458764535520568246&cot=14
2. Let's start button should initiate the "HowTo flow"
| 1.0 | Default fallback flow - 1. create a new template for the fallback message: https://miro.com/app/board/o9J_lttkfEA=/?moveToWidget=3458764535520568246&cot=14
2. Let's start button should initiate the "HowTo flow"
| non_defect | default fallback flow create a new template for the fallback message let s start button should initiate the howto flow | 0 |
134,144 | 18,428,974,442 | IssuesEvent | 2021-10-14 04:18:40 | samq-ghdemo/JS-DEMO | https://api.github.com/repos/samq-ghdemo/JS-DEMO | reopened | CVE-2020-7754 (High) detected in npm-user-validate-0.1.5.tgz | security vulnerability | ## CVE-2020-7754 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>npm-user-validate-0.1.5.tgz</b></p></summary>
<p>User validations for npm</p>
<p>Library home page: <a href="https://re... | True | CVE-2020-7754 (High) detected in npm-user-validate-0.1.5.tgz - ## CVE-2020-7754 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>npm-user-validate-0.1.5.tgz</b></p></summary>
<p>User va... | non_defect | cve high detected in npm user validate tgz cve high severity vulnerability vulnerable library npm user validate tgz user validations for npm library home page a href path to dependency file js demo package json path to vulnerable library js demo node modules npm node... | 0 |
667,895 | 22,513,960,464 | IssuesEvent | 2022-06-24 00:13:06 | acreloaded/acr | https://api.github.com/repos/acreloaded/acr | closed | 164: aiming down sight problem | bug invalid priority-3-high | **aiming down sight problem** by `alex01763`
Issue 164 posted to Google Code on 2014 Jun 26 at 10:01:58
Current status: Invalid
Current labels: `Type-Defect`, `Priority-High`, `Component-Logic`, `Usability`
`alex01763` on 2014 Jun 26 at 10:01:58:
> <b>What steps will reproduce the problem?</b>
> 1.if i aim down my s... | 1.0 | 164: aiming down sight problem - **aiming down sight problem** by `alex01763`
Issue 164 posted to Google Code on 2014 Jun 26 at 10:01:58
Current status: Invalid
Current labels: `Type-Defect`, `Priority-High`, `Component-Logic`, `Usability`
`alex01763` on 2014 Jun 26 at 10:01:58:
> <b>What steps will reproduce the pr... | non_defect | aiming down sight problem aiming down sight problem by issue posted to google code on jun at current status invalid current labels type defect priority high component logic usability on jun at what steps will reproduce the problem if i aim down my sight ... | 0 |
11,073 | 2,632,356,811 | IssuesEvent | 2015-03-08 01:36:29 | marmarek/test | https://api.github.com/repos/marmarek/test | closed | Do not poll iptables_error on stopped firewall vm | C: qubes-manager P: major R: fixed T: defect | **Reported by marmarek on 24 Mar 2011 22:26 UTC**
When firewall vm is stopped, qubes-manager produces:
xenstore-read: couldn't read path /local/domain/-1/qubes_iptables_error | 1.0 | Do not poll iptables_error on stopped firewall vm - **Reported by marmarek on 24 Mar 2011 22:26 UTC**
When firewall vm is stopped, qubes-manager produces:
xenstore-read: couldn't read path /local/domain/-1/qubes_iptables_error | defect | do not poll iptables error on stopped firewall vm reported by marmarek on mar utc when firewall vm is stopped qubes manager produces xenstore read couldn t read path local domain qubes iptables error | 1 |
4,097 | 2,610,087,347 | IssuesEvent | 2015-02-26 18:26:32 | chrsmith/dsdsdaadf | https://api.github.com/repos/chrsmith/dsdsdaadf | opened | 深圳痤疮该怎么治疗 | auto-migrated Priority-Medium Type-Defect | ```
深圳痤疮该怎么治疗【深圳韩方科颜全国热线400-869-1818,24小
时QQ4008691818】深圳韩方科颜专业祛痘连锁机构,机构以韩国��
�方——韩方科颜这一国妆准字号治疗型权威,祛痘佳品,韩�
��科颜专业祛痘连锁机构,采用韩国秘方配合专业“不反弹”
健康祛痘技术并结合先进“先进豪华彩光”仪,开创国内专��
�治疗粉刺、痤疮签约包治先河,成功消除了许多顾客脸上的�
��痘。
```
-----
Original issue reported on code.google.com by `szft...@163.com` on 14 May 2014 at 7:19 | 1.0 | 深圳痤疮该怎么治疗 - ```
深圳痤疮该怎么治疗【深圳韩方科颜全国热线400-869-1818,24小
时QQ4008691818】深圳韩方科颜专业祛痘连锁机构,机构以韩国��
�方——韩方科颜这一国妆准字号治疗型权威,祛痘佳品,韩�
��科颜专业祛痘连锁机构,采用韩国秘方配合专业“不反弹”
健康祛痘技术并结合先进“先进豪华彩光”仪,开创国内专��
�治疗粉刺、痤疮签约包治先河,成功消除了许多顾客脸上的�
��痘。
```
-----
Original issue reported on code.google.com by `szft...@163.com` on 14 May 2014 at 7:19 | defect | 深圳痤疮该怎么治疗 深圳痤疮该怎么治疗【 , 】深圳韩方科颜专业祛痘连锁机构,机构以韩国�� �方——韩方科颜这一国妆准字号治疗型权威,祛痘佳品,韩� ��科颜专业祛痘连锁机构,采用韩国秘方配合专业“不反弹” 健康祛痘技术并结合先进“先进豪华彩光”仪,开创国内专�� �治疗粉刺、痤疮签约包治先河,成功消除了许多顾客脸上的� ��痘。 original issue reported on code google com by szft com on may at | 1 |
18,764 | 3,086,888,909 | IssuesEvent | 2015-08-25 07:58:42 | NamPNQ/html5slides | https://api.github.com/repos/NamPNQ/html5slides | closed | Change Google logo in bottom-right corner? | auto-migrated Priority-Medium Type-Defect | ```
Hi,
I love this HTML5 presentation template and would like to use it, both for an
actual presentation but also to improve my on-hands HTML 5 experience.
Is someone able to tell me where the Google logo in the bottom-right corner is
referenced? I want to change it into something else, but am not able to find it ... | 1.0 | Change Google logo in bottom-right corner? - ```
Hi,
I love this HTML5 presentation template and would like to use it, both for an
actual presentation but also to improve my on-hands HTML 5 experience.
Is someone able to tell me where the Google logo in the bottom-right corner is
referenced? I want to change it int... | defect | change google logo in bottom right corner hi i love this presentation template and would like to use it both for an actual presentation but also to improve my on hands html experience is someone able to tell me where the google logo in the bottom right corner is referenced i want to change it into so... | 1 |
5,989 | 2,610,219,003 | IssuesEvent | 2015-02-26 19:09:38 | chrsmith/somefinders | https://api.github.com/repos/chrsmith/somefinders | opened | русификатор для launch blue manager suite | auto-migrated Priority-Medium Type-Defect | ```
'''Борис Волков'''
Привет всем не подскажите где можно найти
.русификатор для launch blue manager suite. где то
видел уже
'''Валериан Абрамов'''
Вот хороший сайт где можно скачать
http://bit.ly/1aV8gab
'''Витольд Сысоев'''
Просит ввести номер мобилы!Не опасно ли это?
'''Викентий Гусев'''
Неа все ок у меня нич... | 1.0 | русификатор для launch blue manager suite - ```
'''Борис Волков'''
Привет всем не подскажите где можно найти
.русификатор для launch blue manager suite. где то
видел уже
'''Валериан Абрамов'''
Вот хороший сайт где можно скачать
http://bit.ly/1aV8gab
'''Витольд Сысоев'''
Просит ввести номер мобилы!Не опасно ли это?... | defect | русификатор для launch blue manager suite борис волков привет всем не подскажите где можно найти русификатор для launch blue manager suite где то видел уже валериан абрамов вот хороший сайт где можно скачать витольд сысоев просит ввести номер мобилы не опасно ли это викентий гусев ... | 1 |
2,165 | 2,667,072,442 | IssuesEvent | 2015-03-22 06:50:52 | chocolatey/choco | https://api.github.com/repos/chocolatey/choco | closed | Document chocolateyPackageFolder, chocolateyPackageName and chocolateyPackageVersion variables | Documentation | Apparently it is possible to access some nuspec information from within `chocolateyInstall.ps1` and `chocolateyUninstall.ps1` using `$env:chocolateyPackageFolder`, `$env:chocolateyPackageName` and **`$env:chocolateyPackageVersion`** (duplicated in `$env:packageFolder`, `$env:packageName` and `$env:packageVersion`).
... | 1.0 | Document chocolateyPackageFolder, chocolateyPackageName and chocolateyPackageVersion variables - Apparently it is possible to access some nuspec information from within `chocolateyInstall.ps1` and `chocolateyUninstall.ps1` using `$env:chocolateyPackageFolder`, `$env:chocolateyPackageName` and **`$env:chocolateyPackageV... | non_defect | document chocolateypackagefolder chocolateypackagename and chocolateypackageversion variables apparently it is possible to access some nuspec information from within chocolateyinstall and chocolateyuninstall using env chocolateypackagefolder env chocolateypackagename and env chocolateypackageversi... | 0 |
2,955 | 2,607,967,479 | IssuesEvent | 2015-02-26 00:43:02 | chrsmithdemos/leveldb | https://api.github.com/repos/chrsmithdemos/leveldb | opened | Assertion Failure When Closing Database | auto-migrated Priority-Medium Type-Defect | ```
What steps will reproduce the problem?
1.open array of dbs, "db[n]"
2.close db using "delete db[n]"
What is the expected output? What do you see instead?
Expect db to close. Instead, see assertion failure:
main: db/version_set.cc:715: leveldb::VersionSet::~VersionSet(): Assertion
'dummy_versions_.next_ == &dummy_... | 1.0 | Assertion Failure When Closing Database - ```
What steps will reproduce the problem?
1.open array of dbs, "db[n]"
2.close db using "delete db[n]"
What is the expected output? What do you see instead?
Expect db to close. Instead, see assertion failure:
main: db/version_set.cc:715: leveldb::VersionSet::~VersionSet(): As... | defect | assertion failure when closing database what steps will reproduce the problem open array of dbs db close db using delete db what is the expected output what do you see instead expect db to close instead see assertion failure main db version set cc leveldb versionset versionset assertio... | 1 |
105,375 | 13,182,216,462 | IssuesEvent | 2020-08-12 15:26:30 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | opened | Content Revisions for View Payment's Prototype | design vsa vsa-ebenefits | ## Goal
Given feedback, we need to implement the latest content changes for CH31 so the feature is copy complete and ready to go.
## Tasks
- [ ] Take the [recommendations](#) and update the features' prototypes
## Acceptance Criteria
- [ ] The prototypes are updated with the latest recommendations
- [ ] Prototypes a... | 1.0 | Content Revisions for View Payment's Prototype - ## Goal
Given feedback, we need to implement the latest content changes for CH31 so the feature is copy complete and ready to go.
## Tasks
- [ ] Take the [recommendations](#) and update the features' prototypes
## Acceptance Criteria
- [ ] The prototypes are updated w... | non_defect | content revisions for view payment s prototype goal given feedback we need to implement the latest content changes for so the feature is copy complete and ready to go tasks take the and update the features prototypes acceptance criteria the prototypes are updated with the latest recommen... | 0 |
31,485 | 6,538,299,338 | IssuesEvent | 2017-09-01 05:08:52 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | closed | [event-journal] Incorrect UnsupportedOperationException message | Team: Core Type: Defect | https://github.com/hazelcast/hazelcast/blob/843519c75e235bf8e72ad4dd7f760d576cf17b57/hazelcast/src/main/java/com/hazelcast/client/impl/protocol/task/map/MapEventJournalReadTask.java#L65
Misleading statement, should be "Event journal actions are available when cluster version is 3.9 or higher"); | 1.0 | [event-journal] Incorrect UnsupportedOperationException message - https://github.com/hazelcast/hazelcast/blob/843519c75e235bf8e72ad4dd7f760d576cf17b57/hazelcast/src/main/java/com/hazelcast/client/impl/protocol/task/map/MapEventJournalReadTask.java#L65
Misleading statement, should be "Event journal actions are avail... | defect | incorrect unsupportedoperationexception message misleading statement should be event journal actions are available when cluster version is or higher | 1 |
171,808 | 13,249,655,770 | IssuesEvent | 2020-08-19 21:12:47 | sys-bio/roadrunner | https://api.github.com/repos/sys-bio/roadrunner | closed | Need more test models with events | Testing | I looked through the .rrtest files and we only have one model with events: the model from #276. We need more models with events so that I can fix #281 without breaking existing models. (We also have the SBML test suite and any event tests it contains, but I think we need more.)
| 1.0 | Need more test models with events - I looked through the .rrtest files and we only have one model with events: the model from #276. We need more models with events so that I can fix #281 without breaking existing models. (We also have the SBML test suite and any event tests it contains, but I think we need more.)
| non_defect | need more test models with events i looked through the rrtest files and we only have one model with events the model from we need more models with events so that i can fix without breaking existing models we also have the sbml test suite and any event tests it contains but i think we need more | 0 |
81,039 | 30,679,163,974 | IssuesEvent | 2023-07-26 07:59:53 | arescentral/antares | https://api.github.com/repos/arescentral/antares | closed | Ships’ specifications missing in mission overview | Type:Defect Priority:High Complexity:Low | Clicking on a ship’s image while in the mission briefing screens in Ares brings up a window with the specifications of the ship, in Antares nothing happens. | 1.0 | Ships’ specifications missing in mission overview - Clicking on a ship’s image while in the mission briefing screens in Ares brings up a window with the specifications of the ship, in Antares nothing happens. | defect | ships’ specifications missing in mission overview clicking on a ship’s image while in the mission briefing screens in ares brings up a window with the specifications of the ship in antares nothing happens | 1 |
32,108 | 26,430,716,196 | IssuesEvent | 2023-01-14 19:35:37 | UBCSailbot/sailbot_workspace | https://api.github.com/repos/UBCSailbot/sailbot_workspace | closed | Update sailbot_workspace | infrastructure | ### Disadvantages
- Breaks ability to run Raye codebase
- I don’t foresee a need to be able to run Raye and new project code together; the architectures of the 2 projects are different
- Would probably be a pain to figure out ROS 1 bridge
### Advantages
- Would simplify devcontainer and drastically red... | 1.0 | Update sailbot_workspace - ### Disadvantages
- Breaks ability to run Raye codebase
- I don’t foresee a need to be able to run Raye and new project code together; the architectures of the 2 projects are different
- Would probably be a pain to figure out ROS 1 bridge
### Advantages
- Would simplify devco... | non_defect | update sailbot workspace disadvantages breaks ability to run raye codebase i don’t foresee a need to be able to run raye and new project code together the architectures of the projects are different would probably be a pain to figure out ros bridge advantages would simplify devco... | 0 |
21,464 | 3,510,835,962 | IssuesEvent | 2016-01-09 20:11:33 | ariya/phantomjs | https://api.github.com/repos/ariya/phantomjs | closed | JS crash | old.Domain-WebKit old.Status-New old.Type-Defect | PhantomJS binary always crashes on some sites. Looks like JSCore problem.
Example command:
> ../bin/phantomjs rasterize.js http://nohasslecontractorinsurance.com/ test.png
Here is the backtrace:
(gdb) i th
Id Target Id Frame
4 Thread 0x7fffaf3a9700 (LWP 28256) "QThread" 0x00007... | 1.0 | JS crash - PhantomJS binary always crashes on some sites. Looks like JSCore problem.
Example command:
> ../bin/phantomjs rasterize.js http://nohasslecontractorinsurance.com/ test.png
Here is the backtrace:
(gdb) i th
Id Target Id Frame
4 Thread 0x7fffaf3a9700 (LWP 28256) "QThre... | defect | js crash phantomjs binary always crashes on some sites looks like jscore problem example command bin phantomjs rasterize js test png here is the backtrace gdb i th id target id frame thread lwp qthread in select at sysdeps unix syscall template ... | 1 |
277,818 | 30,674,418,378 | IssuesEvent | 2023-07-26 03:08:16 | amaybaum-prod/atom-hopper | https://api.github.com/repos/amaybaum-prod/atom-hopper | closed | spring-web-5.2.22.RELEASE.jar: 1 vulnerabilities (highest severity is: 9.8) - autoclosed | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-web-5.2.22.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Path to dependency file: /adapters/migration/pom.xml</p>
<p>Path to vulnerable library: /atomhopp... | True | spring-web-5.2.22.RELEASE.jar: 1 vulnerabilities (highest severity is: 9.8) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-web-5.2.22.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Path t... | non_defect | spring web release jar vulnerabilities highest severity is autoclosed vulnerable library spring web release jar spring web path to dependency file adapters migration pom xml path to vulnerable library atomhopper target atomhopper snapshot web inf lib spring web ... | 0 |
64,110 | 18,216,693,538 | IssuesEvent | 2021-09-30 05:51:17 | SUI-Components/sui-components | https://api.github.com/repos/SUI-Components/sui-components | opened | Checkbox field - Elements alignment | defect | Component [checkbox field](https://sui-components.vercel.app/workbench/molecule/checkboxField/demo)
**Is your iteration request related to a problem?**
The alignment of the label, help text and check is not ok

**Is your iteration request related to a problem?**
The alignment of the label, help text and check is not ok
 detected in xstream-1.3.1.jar | security vulnerability | ## CVE-2021-21350 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.3.1.jar</b></p></summary>
<p></p>
<p>Path to vulnerable library: 1.jar</p>
<p>
Dependency Hierarchy:
- :x... | True | CVE-2021-21350 (High) detected in xstream-1.3.1.jar - ## CVE-2021-21350 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.3.1.jar</b></p></summary>
<p></p>
<p>Path to vulnerabl... | non_defect | cve high detected in xstream jar cve high severity vulnerability vulnerable library xstream jar path to vulnerable library jar dependency hierarchy x xstream jar vulnerable library found in head commit a href vulnerability details ... | 0 |
59,046 | 17,015,150,900 | IssuesEvent | 2021-07-02 10:54:42 | tomhughes/trac-tickets | https://api.github.com/repos/tomhughes/trac-tickets | opened | Cities disappear in zoom levels 10..13 | Component: opencyclemap Priority: major Type: defect | **[Submitted to the original trac issue database at 11.21am, Sunday, 29th August 2010]**
I was looking at cycle routes between London and Brighton, both very visible in zoom level 9: http://www.openstreetmap.org/?lat=51.06&lon=-0.082&zoom=9&layers=C
One zoom step closer and Brighton disappears completely, replaced ... | 1.0 | Cities disappear in zoom levels 10..13 - **[Submitted to the original trac issue database at 11.21am, Sunday, 29th August 2010]**
I was looking at cycle routes between London and Brighton, both very visible in zoom level 9: http://www.openstreetmap.org/?lat=51.06&lon=-0.082&zoom=9&layers=C
One zoom step closer and ... | defect | cities disappear in zoom levels i was looking at cycle routes between london and brighton both very visible in zoom level one zoom step closer and brighton disappears completely replaced by completely new places very disorienting continue zooming in four more times to level and brighton come... | 1 |
29,520 | 11,758,201,384 | IssuesEvent | 2020-03-13 15:00:42 | SonarSource/sonar-dotnet | https://api.github.com/repos/SonarSource/sonar-dotnet | closed | Fix S2068 FN: Raise issue for literals passed as arguments | Area: C# Area: Security Area: VB.NET Type: False Negative | ### Description
Issue is not raised when hardcoded password is used directly as argument.
### Repro steps
```
Using Conn As SqlConnection = OpenConn("Server=localhost; Database=Test; User=SA; Password=Secret123") ' Noncompliant
End Using
Using Conn As New SqlConnection("Server=localhost; Database=Test; User... | True | Fix S2068 FN: Raise issue for literals passed as arguments - ### Description
Issue is not raised when hardcoded password is used directly as argument.
### Repro steps
```
Using Conn As SqlConnection = OpenConn("Server=localhost; Database=Test; User=SA; Password=Secret123") ' Noncompliant
End Using
Using Con... | non_defect | fix fn raise issue for literals passed as arguments description issue is not raised when hardcoded password is used directly as argument repro steps using conn as sqlconnection openconn server localhost database test user sa password noncompliant end using using conn as new sql... | 0 |
35,449 | 7,745,501,699 | IssuesEvent | 2018-05-29 18:33:16 | extnet/Ext.NET | https://api.github.com/repos/extnet/Ext.NET | opened | SpriteEvents plugin does not work | 4.x defect extjs-test-pending | Found: 4.5.1
Ext.NET forum thread: []()
DrawContainer's SpriteEvents is not working, as can be noticed in the rotate image examples on MVC and WebForms examples explorers:
- [MVC Rotate Image example](http://mvc4.ext.net/#/Draw_Basic/Rotate_Image/)
- [WebForms Rotate Image example](http://examples4.ext.net/#/Draw... | 1.0 | SpriteEvents plugin does not work - Found: 4.5.1
Ext.NET forum thread: []()
DrawContainer's SpriteEvents is not working, as can be noticed in the rotate image examples on MVC and WebForms examples explorers:
- [MVC Rotate Image example](http://mvc4.ext.net/#/Draw_Basic/Rotate_Image/)
- [WebForms Rotate Image exam... | defect | spriteevents plugin does not work found ext net forum thread drawcontainer s spriteevents is not working as can be noticed in the rotate image examples on mvc and webforms examples explorers the events simply do not fire at least under google chrome if using ms edge the same e... | 1 |
30,675 | 5,832,063,451 | IssuesEvent | 2017-05-08 20:53:12 | trailofbits/manticore | https://api.github.com/repos/trailofbits/manticore | closed | Optimization tips documentation | documentation | Would be helpful for users to know how to optimize manticore. Some topics could include
- using hooks to patch out irrelevant code (like printf)
- abandoning states | 1.0 | Optimization tips documentation - Would be helpful for users to know how to optimize manticore. Some topics could include
- using hooks to patch out irrelevant code (like printf)
- abandoning states | non_defect | optimization tips documentation would be helpful for users to know how to optimize manticore some topics could include using hooks to patch out irrelevant code like printf abandoning states | 0 |
56,740 | 15,345,135,271 | IssuesEvent | 2021-02-28 05:19:45 | kohenkatz/appqr | https://api.github.com/repos/kohenkatz/appqr | closed | Failed to open in play store app | Priority-Medium Type-Defect auto-migrated | ```
What steps will reproduce the problem?
1. After Scan and tab the link directly open in default android browser.
2.
3.
What is the expected output? What do you see instead?
Found error in browser said "This web page is not available".
The generated link is "http://market//details?id=com.letsdoitworld.wastemapper"
... | 1.0 | Failed to open in play store app - ```
What steps will reproduce the problem?
1. After Scan and tab the link directly open in default android browser.
2.
3.
What is the expected output? What do you see instead?
Found error in browser said "This web page is not available".
The generated link is "http://market//details... | defect | failed to open in play store app what steps will reproduce the problem after scan and tab the link directly open in default android browser what is the expected output what do you see instead found error in browser said this web page is not available the generated link is what version of th... | 1 |
251,705 | 27,203,829,740 | IssuesEvent | 2023-02-20 11:36:13 | elastic/cloudbeat | https://api.github.com/repos/elastic/cloudbeat | closed | [BUG] Cloudbeat fails to fetch k8s objects on Kubernetes v1.25 | bug Team:Cloud Security triaged | **Describe the bug**
When deploying Cloudbeat / elastic agent on Kubernetes v1.25 k8s objects are failed to be fetched.
According to the logs
"Failed to list *v1beta1.PodSecurityPolicy: the server could not find the requested resource"
According to Kubernetes documentation [PSP is deprecated and removed in v1.25]... | True | [BUG] Cloudbeat fails to fetch k8s objects on Kubernetes v1.25 - **Describe the bug**
When deploying Cloudbeat / elastic agent on Kubernetes v1.25 k8s objects are failed to be fetched.
According to the logs
"Failed to list *v1beta1.PodSecurityPolicy: the server could not find the requested resource"
According to ... | non_defect | cloudbeat fails to fetch objects on kubernetes describe the bug when deploying cloudbeat elastic agent on kubernetes objects are failed to be fetched according to the logs failed to list podsecuritypolicy the server could not find the requested resource according to kubernetes documen... | 0 |
428,552 | 29,997,506,026 | IssuesEvent | 2023-06-26 06:59:41 | ans-coe/terraform-modules | https://api.github.com/repos/ans-coe/terraform-modules | closed | Rename example NSG | documentation good first issue | https://github.com/ans-coe/terraform-modules/blob/51dafae2ac5f3c6da054c3f350858e7bec800819/azure/network-security-group/examples/advanced/main.tf#LL51C1-L51C54
Example gives the NSG the name ${local.resource_prefix}-rg
It should probably be ${local.resource_prefix}-nsg | 1.0 | Rename example NSG - https://github.com/ans-coe/terraform-modules/blob/51dafae2ac5f3c6da054c3f350858e7bec800819/azure/network-security-group/examples/advanced/main.tf#LL51C1-L51C54
Example gives the NSG the name ${local.resource_prefix}-rg
It should probably be ${local.resource_prefix}-nsg | non_defect | rename example nsg example gives the nsg the name local resource prefix rg it should probably be local resource prefix nsg | 0 |
45,913 | 13,055,821,576 | IssuesEvent | 2020-07-30 02:50:16 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | opened | Nuke TWR (Trac #257) | Incomplete Migration Migrated from Trac combo core defect | Migrated from https://code.icecube.wisc.edu/ticket/257
```json
{
"status": "closed",
"changetime": "2019-01-11T21:22:56",
"description": "Kill it. Kill it with fire.",
"reporter": "nega",
"cc": "blaufuss, olivas",
"resolution": "fixed",
"_ts": "1547241776942948",
"component": "com... | 1.0 | Nuke TWR (Trac #257) - Migrated from https://code.icecube.wisc.edu/ticket/257
```json
{
"status": "closed",
"changetime": "2019-01-11T21:22:56",
"description": "Kill it. Kill it with fire.",
"reporter": "nega",
"cc": "blaufuss, olivas",
"resolution": "fixed",
"_ts": "1547241776942948",... | defect | nuke twr trac migrated from json status closed changetime description kill it kill it with fire reporter nega cc blaufuss olivas resolution fixed ts component combo core summary nuke twr ... | 1 |
48,905 | 13,184,771,679 | IssuesEvent | 2020-08-12 20:03:52 | icecube-trac/tix3 | https://api.github.com/repos/icecube-trac/tix3 | opened | clsim doesn't jive with OpenCL Framework (Trac #416) | Incomplete Migration Migrated from Trac combo simulation defect | <details>
<summary>_Migrated from https://code.icecube.wisc.edu/ticket/416
, reported by nega and owned by claudio.kopper_</summary>
<p>
```json
{
"status": "closed",
"changetime": "2012-10-31T18:00:13",
"description": "http://builds.icecube.wisc.edu/builders/quick_simulation_osx_server_10.6.7/builds/50... | 1.0 | clsim doesn't jive with OpenCL Framework (Trac #416) - <details>
<summary>_Migrated from https://code.icecube.wisc.edu/ticket/416
, reported by nega and owned by claudio.kopper_</summary>
<p>
```json
{
"status": "closed",
"changetime": "2012-10-31T18:00:13",
"description": "http://builds.icecube.wisc.ed... | defect | clsim doesn t jive with opencl framework trac migrated from reported by nega and owned by claudio kopper json status closed changetime description reporter nega cc jvs resolution fixed ts component ... | 1 |
72,043 | 23,903,975,438 | IssuesEvent | 2022-09-08 21:45:58 | idaholab/moose | https://api.github.com/repos/idaholab/moose | closed | PerpendicularElectricFieldInterface erroneously does not use free charge | T: defect P: normal C: Modules/Electromagnetics | ## Bug Description
The `PerpendicularElectricFieldInterface` object is supposed to apply a user-supplied free charge parameter when on an interface where free charge should be non-zero.
## Steps to Reproduce
Try to use `PerpendicularElectricFieldInterface` with a `free_charge` parameter set to any number - it wil... | 1.0 | PerpendicularElectricFieldInterface erroneously does not use free charge - ## Bug Description
The `PerpendicularElectricFieldInterface` object is supposed to apply a user-supplied free charge parameter when on an interface where free charge should be non-zero.
## Steps to Reproduce
Try to use `PerpendicularElectr... | defect | perpendicularelectricfieldinterface erroneously does not use free charge bug description the perpendicularelectricfieldinterface object is supposed to apply a user supplied free charge parameter when on an interface where free charge should be non zero steps to reproduce try to use perpendicularelectr... | 1 |
773,083 | 27,145,244,388 | IssuesEvent | 2023-02-16 19:25:58 | trufflesuite/truffle | https://api.github.com/repos/trufflesuite/truffle | closed | tezos: use latest version of smartpy compiler | help wanted priority3 🔧 | - [ ] I've asked for help in the [Truffle Gitter](http://gitter.im/Consensys/truffle) before filing this issue.
---------------------------
## Issue
`truffle@tezos` uses an old version of smartpy compiler and hence does not compile when using a valid contract from the online smartpy editor e.g. any contract th... | 1.0 | tezos: use latest version of smartpy compiler - - [ ] I've asked for help in the [Truffle Gitter](http://gitter.im/Consensys/truffle) before filing this issue.
---------------------------
## Issue
`truffle@tezos` uses an old version of smartpy compiler and hence does not compile when using a valid contract fro... | non_defect | tezos use latest version of smartpy compiler i ve asked for help in the before filing this issue issue truffle tezos uses an old version of smartpy compiler and hence does not compile when using a valid contract from the online smartpy editor e g any contract that ... | 0 |
493,518 | 14,234,012,608 | IssuesEvent | 2020-11-18 13:00:42 | teamforus/forus | https://api.github.com/repos/teamforus/forus | opened | Remove back button from the sign-up flow of providers | Priority: Must have project-100 | ## Main asssignee: @aghimpu
## Context/goal:
https://forus.io/provider/sign-up
- [ ] Remove the back button if no parameters are in the URL
- [ ] If there is a parameter in the URL - show the back button. | 1.0 | Remove back button from the sign-up flow of providers - ## Main asssignee: @aghimpu
## Context/goal:
https://forus.io/provider/sign-up
- [ ] Remove the back button if no parameters are in the URL
- [ ] If there is a parameter in the URL - show the back button. | non_defect | remove back button from the sign up flow of providers main asssignee aghimpu context goal remove the back button if no parameters are in the url if there is a parameter in the url show the back button | 0 |
199,982 | 15,085,287,848 | IssuesEvent | 2021-02-05 18:26:02 | rstudio/rstudio | https://api.github.com/repos/rstudio/rstudio | closed | RStudio's diagnostic engine incorrectly flags whitespace as unnecessary | bug diagnostics test | https://community.rstudio.com/t/the-tidyverse-style-guide-inconsistent-with-rstudio-style-diagnostics/94060
---
### System details
RStudio Edition : Desktop [Open Source]
RStudio Version : 1.4.1522
OS Version : macOS Big Sur 10.16
R Version : R version 4.0.3 (2020-10-10)
The fo... | 1.0 | RStudio's diagnostic engine incorrectly flags whitespace as unnecessary - https://community.rstudio.com/t/the-tidyverse-style-guide-inconsistent-with-rstudio-style-diagnostics/94060
---
### System details
RStudio Edition : Desktop [Open Source]
RStudio Version : 1.4.1522
OS Version : macOS B... | non_defect | rstudio s diagnostic engine incorrectly flags whitespace as unnecessary system details rstudio edition desktop rstudio version os version macos big sur r version r version the following r code is incorrectly diagnosed with unnecessa... | 0 |
143,570 | 11,569,724,782 | IssuesEvent | 2020-02-20 18:06:53 | godaddy-wordpress/coblocks | https://api.github.com/repos/godaddy-wordpress/coblocks | closed | ISBAT ensure the integrity of the Click to Tweet block through automated tests | [Type] Tests | Automated tests need to be added to the `click-to-tweet` block which follow the groundwork from #835.
#### Tests Required:
- [x] The save function
- [x] Block transforms #1184
- [x] Block deprecation #956
#### AC
- Any attribute that modifies the serialized block output needs to have tests.
- Any existing tr... | 1.0 | ISBAT ensure the integrity of the Click to Tweet block through automated tests - Automated tests need to be added to the `click-to-tweet` block which follow the groundwork from #835.
#### Tests Required:
- [x] The save function
- [x] Block transforms #1184
- [x] Block deprecation #956
#### AC
- Any attribute ... | non_defect | isbat ensure the integrity of the click to tweet block through automated tests automated tests need to be added to the click to tweet block which follow the groundwork from tests required the save function block transforms block deprecation ac any attribute that modifies... | 0 |
60,003 | 17,023,308,545 | IssuesEvent | 2021-07-03 01:21:08 | tomhughes/trac-tickets | https://api.github.com/repos/tomhughes/trac-tickets | closed | Crash when undoing selected way and then upload | Component: merkaartor Priority: major Resolution: fixed Type: defect | **[Submitted to the original trac issue database at 9.30pm, Thursday, 9th October 2008]**
* Draw a way with some nodes
* Draw another way with several nodes
* Select that second way
* Undo all the nodes from the second way until the way vanishes
* Upload
```
#0 0x000000000050498d in PropertiesDock::che... | 1.0 | Crash when undoing selected way and then upload - **[Submitted to the original trac issue database at 9.30pm, Thursday, 9th October 2008]**
* Draw a way with some nodes
* Draw another way with several nodes
* Select that second way
* Undo all the nodes from the second way until the way vanishes
* Upload
... | defect | crash when undoing selected way and then upload draw a way with some nodes draw another way with several nodes select that second way undo all the nodes from the second way until the way vanishes upload in propertiesdock checkmenustatus this at propertiesdock cpp ... | 1 |
18,159 | 5,591,497,802 | IssuesEvent | 2017-03-30 00:03:58 | d-ronin/dRonin | https://api.github.com/repos/d-ronin/dRonin | opened | RFC: clang-format GCS | code-cleanup gcs status/request-for-comments | Rather than fighting issues with formatting in PRs etc. let's just get the pain out of the way and clang-format the whole thing in one massive conflicts-with-everything pull. And also a pre-commit hook to check it. Looks like Chromium have been doing this in most of their code for some time and are currently rolling it... | 1.0 | RFC: clang-format GCS - Rather than fighting issues with formatting in PRs etc. let's just get the pain out of the way and clang-format the whole thing in one massive conflicts-with-everything pull. And also a pre-commit hook to check it. Looks like Chromium have been doing this in most of their code for some time and ... | non_defect | rfc clang format gcs rather than fighting issues with formatting in prs etc let s just get the pain out of the way and clang format the whole thing in one massive conflicts with everything pull and also a pre commit hook to check it looks like chromium have been doing this in most of their code for some time and ... | 0 |
338,553 | 10,231,418,188 | IssuesEvent | 2019-08-18 09:14:57 | dailynowco/daily-apps | https://api.github.com/repos/dailynowco/daily-apps | closed | Navigate to publication page when clicking on the logo | Priority: Low Status: Accepted Status: Completed Type: Feature good first issue | When clicking on the publication's logo on a post card the user should be navigated to a page containing only posts from the same publication.
The behavior is identical to clicking on a publication in the side menu.
 | EnergyPlus SeverityMedium WontFix unconfirmed defect | ###### Assigned to: F Buhl
###### Added on 2013-05-28 16:57 by @lklawrie
##
External Ref: yahoo group/personal email
Last build tested: `13.04.30 V8.0.0.008 - rerelease`
| 1.0 | User reports that this file does not work with CalculateFromCircuitLength (CR #9231) - ###### Assigned to: F Buhl
###### Added on 2013-05-28 16:57 by @lklawrie
##
External Ref: yahoo group/personal email
Last build tested: `13.04.30 V8.0.0.008 - rerelease`
| defect | user reports that this file does not work with calculatefromcircuitlength cr assigned to f buhl added on by lklawrie external ref yahoo group personal email last build tested rerelease | 1 |
67,865 | 8,198,865,993 | IssuesEvent | 2018-08-31 17:58:07 | mapbox/mapbox-gl-native | https://api.github.com/repos/mapbox/mapbox-gl-native | opened | Improve visual design of MGLMapSnapshotter’s attribution | design iOS macOS | In `ios-v4.4.0-alpha.2` and earlier, the attribution blob on the image returned by `MGLMapSnapshotter` has [sharp corners](https://github.com/mapbox/mapbox-gl-native/blob/0dac3bc60c549c46f341984439d6fd007fe2ffe6/platform/darwin/src/MGLMapSnapshotter.mm#L372-L401) and [high-opacity black text](https://github.com/mapbox/... | 1.0 | Improve visual design of MGLMapSnapshotter’s attribution - In `ios-v4.4.0-alpha.2` and earlier, the attribution blob on the image returned by `MGLMapSnapshotter` has [sharp corners](https://github.com/mapbox/mapbox-gl-native/blob/0dac3bc60c549c46f341984439d6fd007fe2ffe6/platform/darwin/src/MGLMapSnapshotter.mm#L372-L40... | non_defect | improve visual design of mglmapsnapshotter’s attribution in ios alpha and earlier the attribution blob on the image returned by mglmapsnapshotter has and — let’s round the corners add some vibrancy to the text and perhaps even out the margin spacing cc fabian guerra | 0 |
16,569 | 2,919,015,129 | IssuesEvent | 2015-06-24 11:55:40 | jonkoops/pirate | https://api.github.com/repos/jonkoops/pirate | closed | net framework 3.5 | auto-migrated Priority-Medium Type-Defect | ```
Pirate1010 requires the installation of net framework 3.5
when it will be changed instead to turn even with the net framework 4?
```
Original issue reported on code.google.com by `francobe...@gmail.com` on 29 Apr 2013 at 9:53 | 1.0 | net framework 3.5 - ```
Pirate1010 requires the installation of net framework 3.5
when it will be changed instead to turn even with the net framework 4?
```
Original issue reported on code.google.com by `francobe...@gmail.com` on 29 Apr 2013 at 9:53 | defect | net framework requires the installation of net framework when it will be changed instead to turn even with the net framework original issue reported on code google com by francobe gmail com on apr at | 1 |
26,215 | 4,622,888,072 | IssuesEvent | 2016-09-27 09:09:27 | Openki/Openki | https://api.github.com/repos/Openki/Openki | closed | Retina display (iPad) style issues | defect Mobile Style | - [x] Navbar shadow
- [x] Navbar collapsed for retina displays
- [x] Layout of navbar dropdowns
- [x] ~~Introduction~~ (not a retina specific issue)
- [X] ~~Calendar Submenu~~ (not a retina specific issue)
changes done on https://github.com/schuel/hmmm/tree/styles/retina | 1.0 | Retina display (iPad) style issues - - [x] Navbar shadow
- [x] Navbar collapsed for retina displays
- [x] Layout of navbar dropdowns
- [x] ~~Introduction~~ (not a retina specific issue)
- [X] ~~Calendar Submenu~~ (not a retina specific issue)
changes done on https://github.com/schuel/hmmm/tree/styles/retina | defect | retina display ipad style issues navbar shadow navbar collapsed for retina displays layout of navbar dropdowns introduction not a retina specific issue calendar submenu not a retina specific issue changes done on | 1 |
26,674 | 4,777,409,414 | IssuesEvent | 2016-10-27 16:13:24 | wheeler-microfluidics/microdrop | https://api.github.com/repos/wheeler-microfluidics/microdrop | opened | ExperimentLogController update shows error when it can't find plugin (Trac #131) | defect Incomplete Migration Migrated from Trac | Migrated from http://microfluidics.utoronto.ca/microdrop/ticket/131
```json
{
"status": "new",
"changetime": "2014-03-13T20:00:48",
"description": "[INFO]: [ExperimentLogController].update(): while constructing a Python object\ncannot find module 'plugins.xxx.microdrop' (No module named plugins.xxx)\n in... | 1.0 | ExperimentLogController update shows error when it can't find plugin (Trac #131) - Migrated from http://microfluidics.utoronto.ca/microdrop/ticket/131
```json
{
"status": "new",
"changetime": "2014-03-13T20:00:48",
"description": "[INFO]: [ExperimentLogController].update(): while constructing a Python obj... | defect | experimentlogcontroller update shows error when it can t find plugin trac migrated from json status new changetime description update while constructing a python object ncannot find module plugins xxx microdrop no module named plugins xxx n in li... | 1 |
57,365 | 15,731,613,855 | IssuesEvent | 2021-03-29 17:17:22 | danmar/testissues | https://api.github.com/repos/danmar/testissues | opened | False positive (memory leak) with comma (Trac #386) | False positive Incomplete Migration Migrated from Trac aggro80 defect | Migrated from https://trac.cppcheck.net/ticket/386
```json
{
"status": "closed",
"changetime": "2009-06-10T21:14:28",
"description": "Hi,\n\nThis code produce a false positive.\n\n{{{\nint main()\n{\n double * foo = new double[10];\n double * bar = new double[10];\n\n delete [] foo, delete [] bar;\n\n ... | 1.0 | False positive (memory leak) with comma (Trac #386) - Migrated from https://trac.cppcheck.net/ticket/386
```json
{
"status": "closed",
"changetime": "2009-06-10T21:14:28",
"description": "Hi,\n\nThis code produce a false positive.\n\n{{{\nint main()\n{\n double * foo = new double[10];\n double * bar = n... | defect | false positive memory leak with comma trac migrated from json status closed changetime description hi n nthis code produce a false positive n n nint main n n double foo new double n double bar new double n n delete foo delete bar n n ... | 1 |
19,726 | 3,249,302,986 | IssuesEvent | 2015-10-18 02:05:08 | TASVideos/BizHawk | https://api.github.com/repos/TASVideos/BizHawk | closed | SNES Hires / Laced modes Jumpy | auto-migrated Core-BSNES Type-Defect | ```
What steps will reproduce the problem?
1. Load Power Drive
2. Watch Intro
3. or play for a bit and view car repair screen.
What is the expected output? What do you see instead?
I expect to see a steady image. Instead these hires (laced?) screens are
jumpy. The effect can be seen on
What version of the product... | 1.0 | SNES Hires / Laced modes Jumpy - ```
What steps will reproduce the problem?
1. Load Power Drive
2. Watch Intro
3. or play for a bit and view car repair screen.
What is the expected output? What do you see instead?
I expect to see a steady image. Instead these hires (laced?) screens are
jumpy. The effect can be seen... | defect | snes hires laced modes jumpy what steps will reproduce the problem load power drive watch intro or play for a bit and view car repair screen what is the expected output what do you see instead i expect to see a steady image instead these hires laced screens are jumpy the effect can be seen... | 1 |
69,441 | 22,353,873,092 | IssuesEvent | 2022-06-15 14:11:20 | makedeb/makedeb | https://api.github.com/repos/makedeb/makedeb | opened | Commit fragment fails for git | T-Defect | ### Issue
If you give a commit fragment for a git source, it fails with error `fatal: Remote branch ${commit_sha} not found in upstream origin`.
Example PKGBUILD
```
# Maintainer: Bruno Pagani <archange@archlinux.org>
pkgname=libyuv
pkgver=1+30f9b28
pkgrel=1
pkgdesc="Library for YUV scaling"
arch=(amd64)... | 1.0 | Commit fragment fails for git - ### Issue
If you give a commit fragment for a git source, it fails with error `fatal: Remote branch ${commit_sha} not found in upstream origin`.
Example PKGBUILD
```
# Maintainer: Bruno Pagani <archange@archlinux.org>
pkgname=libyuv
pkgver=1+30f9b28
pkgrel=1
pkgdesc="Librar... | defect | commit fragment fails for git issue if you give a commit fragment for a git source it fails with error fatal remote branch commit sha not found in upstream origin example pkgbuild maintainer bruno pagani pkgname libyuv pkgver pkgrel pkgdesc library for yuv scaling arch ... | 1 |
43,820 | 11,857,459,769 | IssuesEvent | 2020-03-25 09:37:37 | cakephp/cakephp | https://api.github.com/repos/cakephp/cakephp | closed | BinaryUUIDs shouldnt be logged in binary | defect | This is a (multiple allowed):
* [x] bug
* [x] enhancement
* CakePHP Version: master
### What you did
Working with binary-16 UUID (type `binaryuuid`) columns in a Cake4 app.
### What happened
... | 1.0 | BinaryUUIDs shouldnt be logged in binary - This is a (multiple allowed):
* [x] bug
* [x] enhancement
* CakePHP Version: master
### What you did
Working with binary-16 UUID (type `binaryuuid`) columns in a Cake4 app.
### What happened
 detected in https-proxy-agent-1.0.0.tgz | security vulnerability | ## CVE-2018-3739 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>https-proxy-agent-1.0.0.tgz</b></p></summary>
<p>An HTTP(s) proxy `http.Agent` implementation for HTTPS</p>
<p>Library ... | True | CVE-2018-3739 (High) detected in https-proxy-agent-1.0.0.tgz - ## CVE-2018-3739 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>https-proxy-agent-1.0.0.tgz</b></p></summary>
<p>An HTTP... | non_defect | cve high detected in https proxy agent tgz cve high severity vulnerability vulnerable library https proxy agent tgz an http s proxy http agent implementation for https library home page a href dependency hierarchy protractor tgz root library sauce... | 0 |
6,680 | 2,610,259,010 | IssuesEvent | 2015-02-26 19:22:36 | chrsmith/dsdsdaadf | https://api.github.com/repos/chrsmith/dsdsdaadf | opened | 深圳结节性痤疮怎么治 | auto-migrated Priority-Medium Type-Defect | ```
深圳结节性痤疮怎么治【深圳韩方科颜全国热线400-869-1818,24
小时QQ4008691818】深圳韩方科颜专业祛痘连锁机构,机构以韩��
�秘方——韩方科颜这一国妆准字号治疗型权威,祛痘佳品,�
��方科颜专业祛痘连锁机构,采用韩国秘方配合专业“不反弹
”健康祛痘技术并结合先进“先进豪华彩光”仪,开创国内��
�业治疗粉刺、痤疮签约包治先河,成功消除了许多顾客脸上�
��痘痘。
```
-----
Original issue reported on code.google.com by `szft...@163.com` on 14 May 2014 at 8:55 | 1.0 | 深圳结节性痤疮怎么治 - ```
深圳结节性痤疮怎么治【深圳韩方科颜全国热线400-869-1818,24
小时QQ4008691818】深圳韩方科颜专业祛痘连锁机构,机构以韩��
�秘方——韩方科颜这一国妆准字号治疗型权威,祛痘佳品,�
��方科颜专业祛痘连锁机构,采用韩国秘方配合专业“不反弹
”健康祛痘技术并结合先进“先进豪华彩光”仪,开创国内��
�业治疗粉刺、痤疮签约包治先河,成功消除了许多顾客脸上�
��痘痘。
```
-----
Original issue reported on code.google.com by `szft...@163.com` on 14 May 2014 at 8:55 | defect | 深圳结节性痤疮怎么治 深圳结节性痤疮怎么治【 , 】深圳韩方科颜专业祛痘连锁机构,机构以韩�� �秘方——韩方科颜这一国妆准字号治疗型权威,祛痘佳品,� ��方科颜专业祛痘连锁机构,采用韩国秘方配合专业“不反弹 ”健康祛痘技术并结合先进“先进豪华彩光”仪,开创国内�� �业治疗粉刺、痤疮签约包治先河,成功消除了许多顾客脸上� ��痘痘。 original issue reported on code google com by szft com on may at | 1 |
13,975 | 2,789,818,185 | IssuesEvent | 2015-05-08 21:41:22 | google/google-visualization-api-issues | https://api.github.com/repos/google/google-visualization-api-issues | closed | BUG: [GeoMap] Not wokring for City view with more than 5 rows in dataset | Priority-High Type-Defect | Original [issue 199](https://code.google.com/p/google-visualization-api-issues/issues/detail?id=199) created by orwant on 2010-02-18T17:40:20.000Z:
<b>What steps will reproduce the problem? Please provide a link to a</b>
<b>demonstration page if at all possible, or attach code.</b>
1. Open the attached file. It has 5 ... | 1.0 | BUG: [GeoMap] Not wokring for City view with more than 5 rows in dataset - Original [issue 199](https://code.google.com/p/google-visualization-api-issues/issues/detail?id=199) created by orwant on 2010-02-18T17:40:20.000Z:
<b>What steps will reproduce the problem? Please provide a link to a</b>
<b>demonstration page i... | defect | bug not wokring for city view with more than rows in dataset original created by orwant on what steps will reproduce the problem please provide a link to a demonstration page if at all possible or attach code open the attached file it has rows in the dataset it works now unc... | 1 |
81,576 | 31,033,079,567 | IssuesEvent | 2023-08-10 13:40:08 | TykTechnologies/tyk-operator | https://api.github.com/repos/TykTechnologies/tyk-operator | opened | Only first certificate of certificate_secret_names is assigned to API | defect | When defining multiple `certificate_secrets_names` on an `ApiDefinition` it seems only the first one is actually assigned to the API by the operator.
Providing this in the `ApiDefinition` resource:
```yaml
certificate_secret_names:
- cert1-secret
- cert2-secret
```
Results in an API with only the firs... | 1.0 | Only first certificate of certificate_secret_names is assigned to API - When defining multiple `certificate_secrets_names` on an `ApiDefinition` it seems only the first one is actually assigned to the API by the operator.
Providing this in the `ApiDefinition` resource:
```yaml
certificate_secret_names:
- cer... | defect | only first certificate of certificate secret names is assigned to api when defining multiple certificate secrets names on an apidefinition it seems only the first one is actually assigned to the api by the operator providing this in the apidefinition resource yaml certificate secret names s... | 1 |
74,923 | 25,406,198,796 | IssuesEvent | 2022-11-22 15:27:58 | jOOQ/jOOQ | https://api.github.com/repos/jOOQ/jOOQ | closed | Median emulation ignores FILTER and OVER clauses | T: Defect C: Functionality P: Medium E: All Editions | ### Expected behavior
When using `median($field).filterWhere(condition)` with Postgres Dialect, the filter-condition should either be applied or it should not compile or at least an error should be thrown.
There should also be a way to opt out of the median emulation for higher postgres version where median can be ... | 1.0 | Median emulation ignores FILTER and OVER clauses - ### Expected behavior
When using `median($field).filterWhere(condition)` with Postgres Dialect, the filter-condition should either be applied or it should not compile or at least an error should be thrown.
There should also be a way to opt out of the median emulati... | defect | median emulation ignores filter and over clauses expected behavior when using median field filterwhere condition with postgres dialect the filter condition should either be applied or it should not compile or at least an error should be thrown there should also be a way to opt out of the median emulati... | 1 |
424,504 | 12,312,090,290 | IssuesEvent | 2020-05-12 13:26:53 | jenkins-x/jx | https://api.github.com/repos/jenkins-x/jx | closed | jx install --provider=eks fails 403 route53:ListHostedZones when using diferent AWS profile | area/eks kind/enhancement lifecycle/rotten priority/important-longterm | ### Summary
I have an AWS user that has permission to assume other roles for other accounts, so with this same user I can authenticate and operate switching accounts, switching the profile configured to assume other roles.
When trying to install jx on a running cluster in an other account using an alternate profil... | 1.0 | jx install --provider=eks fails 403 route53:ListHostedZones when using diferent AWS profile - ### Summary
I have an AWS user that has permission to assume other roles for other accounts, so with this same user I can authenticate and operate switching accounts, switching the profile configured to assume other roles.
... | non_defect | jx install provider eks fails listhostedzones when using diferent aws profile summary i have an aws user that has permission to assume other roles for other accounts so with this same user i can authenticate and operate switching accounts switching the profile configured to assume other roles when t... | 0 |
24,592 | 4,029,603,836 | IssuesEvent | 2016-05-18 11:20:25 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | closed | Cache should not expire entites when Duration value is 0 (zero) | Team: Integration Type: Defect | According to the JCache API javadoc, when the durationAmount parameter in ` javax.cache.expiry.Duration` constructor is set to 0 (zero), it means cache entites should live eternal. Here is the javadoc:
```
/**
* Constructs a duration.
*
* @param timeUnit the unit of time to specify time in. The ... | 1.0 | Cache should not expire entites when Duration value is 0 (zero) - According to the JCache API javadoc, when the durationAmount parameter in ` javax.cache.expiry.Duration` constructor is set to 0 (zero), it means cache entites should live eternal. Here is the javadoc:
```
/**
* Constructs a duration.
*
... | defect | cache should not expire entites when duration value is zero according to the jcache api javadoc when the durationamount parameter in javax cache expiry duration constructor is set to zero it means cache entites should live eternal here is the javadoc constructs a duration ... | 1 |
21,921 | 18,074,009,442 | IssuesEvent | 2021-09-21 07:48:30 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | Tab key can't be used in editor shortcuts. | bug topic:editor usability | **Operating system or device - Godot version:**
Linux - Master
**Issue description:**
When pressing an Editor shortcut that involves the `Tab` key, Godot will focus the next `control` instead of activating the shortcut. Easily testable with the default "next/prev scene" shortcut.
**Steps to reproduce:**
- Ha... | True | Tab key can't be used in editor shortcuts. - **Operating system or device - Godot version:**
Linux - Master
**Issue description:**
When pressing an Editor shortcut that involves the `Tab` key, Godot will focus the next `control` instead of activating the shortcut. Easily testable with the default "next/prev scene"... | non_defect | tab key can t be used in editor shortcuts operating system or device godot version linux master issue description when pressing an editor shortcut that involves the tab key godot will focus the next control instead of activating the shortcut easily testable with the default next prev scene ... | 0 |
4,856 | 2,610,158,491 | IssuesEvent | 2015-02-26 18:50:18 | chrsmith/republic-at-war | https://api.github.com/repos/chrsmith/republic-at-war | closed | MTT | auto-migrated Priority-Medium Type-Defect | ```
change icon for MTT deploy
```
-----
Original issue reported on code.google.com by `z3r0...@gmail.com` on 30 Jan 2011 at 3:02 | 1.0 | MTT - ```
change icon for MTT deploy
```
-----
Original issue reported on code.google.com by `z3r0...@gmail.com` on 30 Jan 2011 at 3:02 | defect | mtt change icon for mtt deploy original issue reported on code google com by gmail com on jan at | 1 |
134,375 | 12,602,031,310 | IssuesEvent | 2020-06-11 10:56:48 | GhRoadDemo/ghroaddemo | https://api.github.com/repos/GhRoadDemo/ghroaddemo | closed | Content missing about organizations | documentation | There is no information about organisations in the readme file | 1.0 | Content missing about organizations - There is no information about organisations in the readme file | non_defect | content missing about organizations there is no information about organisations in the readme file | 0 |
6,602 | 2,610,257,600 | IssuesEvent | 2015-02-26 19:22:12 | chrsmith/dsdsdaadf | https://api.github.com/repos/chrsmith/dsdsdaadf | opened | 深圳激光去痘印多少钱 | auto-migrated Priority-Medium Type-Defect | ```
深圳激光去痘印多少钱【深圳韩方科颜全国热线400-869-1818,24
小时QQ4008691818】深圳韩方科颜专业祛痘连锁机构,机构以韩��
�秘方——韩方科颜这一国妆准字号治疗型权威,祛痘佳品,�
��方科颜专业祛痘连锁机构,采用韩国秘方配合专业“不反弹
”健康祛痘技术并结合先进“先进豪华彩光”仪,开创国内��
�业治疗粉刺、痤疮签约包治先河,成功消除了许多顾客脸上�
��痘痘。
```
-----
Original issue reported on code.google.com by `szft...@163.com` on 14 May 2014 at 8:43 | 1.0 | 深圳激光去痘印多少钱 - ```
深圳激光去痘印多少钱【深圳韩方科颜全国热线400-869-1818,24
小时QQ4008691818】深圳韩方科颜专业祛痘连锁机构,机构以韩��
�秘方——韩方科颜这一国妆准字号治疗型权威,祛痘佳品,�
��方科颜专业祛痘连锁机构,采用韩国秘方配合专业“不反弹
”健康祛痘技术并结合先进“先进豪华彩光”仪,开创国内��
�业治疗粉刺、痤疮签约包治先河,成功消除了许多顾客脸上�
��痘痘。
```
-----
Original issue reported on code.google.com by `szft...@163.com` on 14 May 2014 at 8:43 | defect | 深圳激光去痘印多少钱 深圳激光去痘印多少钱【 , 】深圳韩方科颜专业祛痘连锁机构,机构以韩�� �秘方——韩方科颜这一国妆准字号治疗型权威,祛痘佳品,� ��方科颜专业祛痘连锁机构,采用韩国秘方配合专业“不反弹 ”健康祛痘技术并结合先进“先进豪华彩光”仪,开创国内�� �业治疗粉刺、痤疮签约包治先河,成功消除了许多顾客脸上� ��痘痘。 original issue reported on code google com by szft com on may at | 1 |
71,479 | 23,644,817,964 | IssuesEvent | 2022-08-25 20:49:41 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | The "useLatestResult should return results" test is flaky | T-Defect S-Major A-Testing A-Developer-Experience O-Uncommon Z-Flaky-Test | https://buildkite.com/organizations/matrix-dot-org/pipelines/matrix-react-sdk/builds/27666/jobs/01826ebd-c9d4-44d3-a483-c8aaf6182539/raw_log
```
Summary of all failing tests
FAIL test/hooks/useLatestResult-test.tsx
● useLatestResult › should return results
expect(received).toEqual(expected) // deep eq... | 1.0 | The "useLatestResult should return results" test is flaky - https://buildkite.com/organizations/matrix-dot-org/pipelines/matrix-react-sdk/builds/27666/jobs/01826ebd-c9d4-44d3-a483-c8aaf6182539/raw_log
```
Summary of all failing tests
FAIL test/hooks/useLatestResult-test.tsx
● useLatestResult › should return r... | defect | the uselatestresult should return results test is flaky summary of all failing tests fail test hooks uselatestresult test tsx ● uselatestresult › should return results expect received toequal expected deep equality expected received await... | 1 |
252,879 | 19,074,733,058 | IssuesEvent | 2021-11-27 15:10:06 | mit-ll-responsible-ai/hydra-zen | https://api.github.com/repos/mit-ll-responsible-ai/hydra-zen | closed | Make a note about `defaults` in our config-groups tutorial | documentation | Working through [this](https://mit-ll-responsible-ai.github.io/hydra-zen/tutorials/config_groups.html) tutorial has the user configure a `defaults` field:
```python
Config = make_config("player", defaults=["_self_", {"player": "base"}])
```
a reader might naturally look to `make_config`'s docs for explanation..... | 1.0 | Make a note about `defaults` in our config-groups tutorial - Working through [this](https://mit-ll-responsible-ai.github.io/hydra-zen/tutorials/config_groups.html) tutorial has the user configure a `defaults` field:
```python
Config = make_config("player", defaults=["_self_", {"player": "base"}])
```
a reader ... | non_defect | make a note about defaults in our config groups tutorial working through tutorial has the user configure a defaults field python config make config player defaults a reader might naturally look to make config s docs for explanation but there is none since we don t give that field ... | 0 |
137,594 | 20,170,043,866 | IssuesEvent | 2022-02-10 09:36:14 | saySthAbout/NewPlace-FrontEnd | https://api.github.com/repos/saySthAbout/NewPlace-FrontEnd | closed | main 레이아웃 제작 | Design/UX | ## 필요한 기능
반응형 header, bottomMenu, footer에 의해 무너지지 않는(겹침 현상이 없는) main 영역 레이아웃 만들기
| 1.0 | main 레이아웃 제작 - ## 필요한 기능
반응형 header, bottomMenu, footer에 의해 무너지지 않는(겹침 현상이 없는) main 영역 레이아웃 만들기
| non_defect | main 레이아웃 제작 필요한 기능 반응형 header bottommenu footer에 의해 무너지지 않는 겹침 현상이 없는 main 영역 레이아웃 만들기 | 0 |
137,052 | 11,097,825,807 | IssuesEvent | 2019-12-16 14:07:13 | zeebe-io/zeebe | https://api.github.com/repos/zeebe-io/zeebe | closed | LogStreamTest.shouldCloseLogStream unstabled | Status: Needs Review Type: Maintenance Type: Unstable Test | **Description**
Failed sometimes in the CI.
```
[ERROR] Tests run: 4, Failures: 1, Errors: 0, Skipped: 0, Time elapsed: 2.074 s <<< FAILURE! - in io.zeebe.logstreams.log.LogStreamTest
[ERROR] io.zeebe.logstreams.log.LogStreamTest.shouldCloseLogStream Time elapsed: 0.683 s <<< FAILURE!
java.lang.Asserti... | 1.0 | LogStreamTest.shouldCloseLogStream unstabled - **Description**
Failed sometimes in the CI.
```
[ERROR] Tests run: 4, Failures: 1, Errors: 0, Skipped: 0, Time elapsed: 2.074 s <<< FAILURE! - in io.zeebe.logstreams.log.LogStreamTest
[ERROR] io.zeebe.logstreams.log.LogStreamTest.shouldCloseLogStream Time elap... | non_defect | logstreamtest shouldcloselogstream unstabled description failed sometimes in the ci tests run failures errors skipped time elapsed s failure in io zeebe logstreams log logstreamtest io zeebe logstreams log logstreamtest shouldcloselogstream time elapsed s ... | 0 |
82,027 | 31,860,003,846 | IssuesEvent | 2023-09-15 10:11:58 | scipy/scipy | https://api.github.com/repos/scipy/scipy | opened | BUG: upcasting of indices dtype from DIA to COO/CSR/BSR arrays | defect | ### Describe your issue.
While I understand the decision of not using downcasting for indices (cf. https://github.com/scipy/scipy/pull/18509), it seems that the conversion from DIA to COO/CSR/BSR matrices will make an upcast from `np.int32` to `np.int64` while it should not be needed. I assume that using the `dtype` o... | 1.0 | BUG: upcasting of indices dtype from DIA to COO/CSR/BSR arrays - ### Describe your issue.
While I understand the decision of not using downcasting for indices (cf. https://github.com/scipy/scipy/pull/18509), it seems that the conversion from DIA to COO/CSR/BSR matrices will make an upcast from `np.int32` to `np.int64`... | defect | bug upcasting of indices dtype from dia to coo csr bsr arrays describe your issue while i understand the decision of not using downcasting for indices cf it seems that the conversion from dia to coo csr bsr matrices will make an upcast from np to np while it should not be needed i assume that usin... | 1 |
457,247 | 13,153,751,090 | IssuesEvent | 2020-08-10 04:38:24 | grafana/grafana | https://api.github.com/repos/grafana/grafana | closed | global built-in variables: __dashboard and __dashboard.name are not available in the text panel | area/dashboard/templating priority/important-soon type/bug | I want to use the relatively new global variable __dashboard to open git hub issues.
When I try to use the variable in the panel it is not being replaced, I've tried both the `$` and the `[[]]` substitution none worked
How I just reproduce it:
* Edit a text panel and add ${__dashboard.name} in the text - Should ... | 1.0 | global built-in variables: __dashboard and __dashboard.name are not available in the text panel - I want to use the relatively new global variable __dashboard to open git hub issues.
When I try to use the variable in the panel it is not being replaced, I've tried both the `$` and the `[[]]` substitution none worked
... | non_defect | global built in variables dashboard and dashboard name are not available in the text panel i want to use the relatively new global variable dashboard to open git hub issues when i try to use the variable in the panel it is not being replaced i ve tried both the and the substitution none worked h... | 0 |
19,163 | 3,146,558,050 | IssuesEvent | 2015-09-14 23:59:32 | dart-lang/sdk | https://api.github.com/repos/dart-lang/sdk | opened | VM service: stdout doesn't produce WriteEvents | Area-Observatory Type-Defect | Currently only `print()` produces `WriteEvent`s on the `Stdout` stream; `dart:io`'s `stdout.add()` and derived methods don't. `stderr` produces `WriteEvent`s on `Stderr` as expected. | 1.0 | VM service: stdout doesn't produce WriteEvents - Currently only `print()` produces `WriteEvent`s on the `Stdout` stream; `dart:io`'s `stdout.add()` and derived methods don't. `stderr` produces `WriteEvent`s on `Stderr` as expected. | defect | vm service stdout doesn t produce writeevents currently only print produces writeevent s on the stdout stream dart io s stdout add and derived methods don t stderr produces writeevent s on stderr as expected | 1 |
6,396 | 2,610,242,211 | IssuesEvent | 2015-02-26 19:17:06 | chrsmith/jsjsj122 | https://api.github.com/repos/chrsmith/jsjsj122 | opened | 台州割包皮包茎哪家专业 | auto-migrated Priority-Medium Type-Defect | ```
台州割包皮包茎哪家专业【台州五洲生殖医院】24小时健康咨
询热线:0576-88066933-(扣扣800080609)-(微信号tzwzszyy)医院地址:台州
市椒江区枫南路229号(枫南大转盘旁)乘车线路:乘坐104、108�
��118、198及椒江一金清公交车直达枫南小区,乘坐107、105、109
、112、901、 902公交车到星星广场下车,步行即可到院。
诊疗项目:阳痿,早泄,前列腺炎,前列腺增生,龟头炎,��
�精,无精。包皮包茎,精索静脉曲张,淋病等。
台州五洲生殖医院是台州最大的男科医院,权威专家在线免��
�咨询,拥有专业完善的男科检查治疗设备,严格按照国家标�
��收费。尖端医疗设备,与世界同步。... | 1.0 | 台州割包皮包茎哪家专业 - ```
台州割包皮包茎哪家专业【台州五洲生殖医院】24小时健康咨
询热线:0576-88066933-(扣扣800080609)-(微信号tzwzszyy)医院地址:台州
市椒江区枫南路229号(枫南大转盘旁)乘车线路:乘坐104、108�
��118、198及椒江一金清公交车直达枫南小区,乘坐107、105、109
、112、901、 902公交车到星星广场下车,步行即可到院。
诊疗项目:阳痿,早泄,前列腺炎,前列腺增生,龟头炎,��
�精,无精。包皮包茎,精索静脉曲张,淋病等。
台州五洲生殖医院是台州最大的男科医院,权威专家在线免��
�咨询,拥有专业完善的男科检查治疗设备,严格按照国家标�
��收费... | defect | 台州割包皮包茎哪家专业 台州割包皮包茎哪家专业【台州五洲生殖医院】 询热线 微信号tzwzszyy 医院地址 台州 (枫南大转盘旁)乘车线路 、 � �� 、 , 、 、 、 、 、 ,步行即可到院。 诊疗项目:阳痿,早泄,前列腺炎,前列腺增生,龟头炎,�� �精,无精。包皮包茎,精索静脉曲张,淋病等。 台州五洲生殖医院是台州最大的男科医院,权威专家在线免�� �咨询,拥有专业完善的男科检查治疗设备,严格按照国家标� ��收费。尖端医疗设备,与世界同步。权威专家,成就专业典 范。人性化服务,一切以患者为中心。 看男科就选台州五洲生殖医院,专业男科为男人。 origina... | 1 |
91,624 | 10,724,325,718 | IssuesEvent | 2019-10-28 01:00:28 | scipy/scipy | https://api.github.com/repos/scipy/scipy | closed | Typo in sp.stats.wilcoxon docstring | Documentation scipy.stats | The docstring of [sp.stats.wilcoxon](https://docs.scipy.org/doc/scipy/reference/generated/scipy.stats.wilcoxon.html) has a jumbled sentence:
> The one-sided test has the null that the median is positive against the alternative that the it is negative (alternative == 'less'), or vice versa (alternative == 'greater.').... | 1.0 | Typo in sp.stats.wilcoxon docstring - The docstring of [sp.stats.wilcoxon](https://docs.scipy.org/doc/scipy/reference/generated/scipy.stats.wilcoxon.html) has a jumbled sentence:
> The one-sided test has the null that the median is positive against the alternative that the it is negative (alternative == 'less'), or v... | non_defect | typo in sp stats wilcoxon docstring the docstring of has a jumbled sentence the one sided test has the null that the median is positive against the alternative that the it is negative alternative less or vice versa alternative greater scipy numpy python version information scipy ... | 0 |
15,931 | 2,869,099,552 | IssuesEvent | 2015-06-05 23:19:56 | dart-lang/sdk | https://api.github.com/repos/dart-lang/sdk | closed | Calling toUpperCase on null | Area-Pkg Pkg-Unittest Priority-Unassigned Triaged Type-Defect | The unittest package is calling the toUpperCase method while formatting test results. In certain situations it ends up with calling toUpperCase on a null object.
See for example the log below from http://build.chromium.org/p/client.dart/builders/vm-arm-sim-debug-be/builds/1098/steps/tests/logs/stdio
FAILED: none-vm d... | 1.0 | Calling toUpperCase on null - The unittest package is calling the toUpperCase method while formatting test results. In certain situations it ends up with calling toUpperCase on a null object.
See for example the log below from http://build.chromium.org/p/client.dart/builders/vm-arm-sim-debug-be/builds/1098/steps/tests... | defect | calling touppercase on null the unittest package is calling the touppercase method while formatting test results in certain situations it ends up with calling touppercase on a null object see for example the log below from failed none vm debug simarm pkg code transformers test resolver test expected pass act... | 1 |
33,699 | 7,198,582,128 | IssuesEvent | 2018-02-05 13:22:05 | ShaikASK/Testing | https://api.github.com/repos/ShaikASK/Testing | opened | Intro page::Safari::Header section content is being overlapping with the background image | Defect P1 SumFive Team | Steps To Replicate :
1. Launch the url :
2. Login as HR Admin user
3. Navigate to 'Settings' menu
4. Select "Intro Page" from the menu options
5. Click on add (+)
6. Select an option / any company name from the dropdown list
7. Click on 'Edit' option displayed in logo section
8. Provide full length content ... | 1.0 | Intro page::Safari::Header section content is being overlapping with the background image - Steps To Replicate :
1. Launch the url :
2. Login as HR Admin user
3. Navigate to 'Settings' menu
4. Select "Intro Page" from the menu options
5. Click on add (+)
6. Select an option / any company name from the dropdow... | defect | intro page safari header section content is being overlapping with the background image steps to replicate launch the url login as hr admin user navigate to settings menu select intro page from the menu options click on add select an option any company name from the dropdow... | 1 |
47,691 | 13,066,101,116 | IssuesEvent | 2020-07-30 20:59:58 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | closed | [sim-services] Documentation is horrible (Trac #998) | Migrated from Trac combo simulation defect | Most modules are not documented at all. This needs to be fixed before the next release.
Migrated from https://code.icecube.wisc.edu/ticket/998
```json
{
"status": "closed",
"changetime": "2016-03-18T21:14:03",
"description": "Most modules are not documented at all. This needs to be fixed before the nex... | 1.0 | [sim-services] Documentation is horrible (Trac #998) - Most modules are not documented at all. This needs to be fixed before the next release.
Migrated from https://code.icecube.wisc.edu/ticket/998
```json
{
"status": "closed",
"changetime": "2016-03-18T21:14:03",
"description": "Most modules are not do... | defect | documentation is horrible trac most modules are not documented at all this needs to be fixed before the next release migrated from json status closed changetime description most modules are not documented at all this needs to be fixed before the next release... | 1 |
6,324 | 3,010,620,560 | IssuesEvent | 2015-07-28 14:08:49 | JuliaFEM/JuliaFEM.jl | https://api.github.com/repos/JuliaFEM/JuliaFEM.jl | closed | juliafem.org icon | documentation | Hi,
We would need to add this code to our html page:
```html
<link rel="icon" type="image/png" href="https://github.com/JuliaFEM/JuliaFEM.jl/blob/master/docs/logo/JuliaFEMLogo_32x32.png" sizes="32x32" />
<link rel="icon" type="image/png" href="https://github.com/JuliaFEM/JuliaFEM.jl/blob/master/docs/logo/JuliaFEMLo... | 1.0 | juliafem.org icon - Hi,
We would need to add this code to our html page:
```html
<link rel="icon" type="image/png" href="https://github.com/JuliaFEM/JuliaFEM.jl/blob/master/docs/logo/JuliaFEMLogo_32x32.png" sizes="32x32" />
<link rel="icon" type="image/png" href="https://github.com/JuliaFEM/JuliaFEM.jl/blob/master/... | non_defect | juliafem org icon hi we would need to add this code to our html page html of course you can replace the full path with a relative path as well if you know the relative path this would change the kapsi logo to juliafem logo in your browser tab | 0 |
15,109 | 3,925,347,361 | IssuesEvent | 2016-04-22 18:36:49 | diana-hep/carl | https://api.github.com/repos/diana-hep/carl | opened | Notebook: probability calibration | Documentation Enhancement | Would nice to add a notebook illustrating the usage of `CalibratedClassifierCV`. | 1.0 | Notebook: probability calibration - Would nice to add a notebook illustrating the usage of `CalibratedClassifierCV`. | non_defect | notebook probability calibration would nice to add a notebook illustrating the usage of calibratedclassifiercv | 0 |
10,816 | 2,622,191,447 | IssuesEvent | 2015-03-04 00:23:15 | byzhang/cudpp | https://api.github.com/repos/byzhang/cudpp | closed | cudpp1.1.1 with cuda3.1 on ubuntu9.10 ../cudpp/make takes a long long time | auto-migrated Priority-Medium Type-Defect | ```
What steps will reproduce the problem?
1.download and install cuda 3.1 (first the driver-> toolkit ->sdk) on ubuntu
9.10
2.compile sdk
3.download cudpp1.1.1 and place in /usr/local/cudpp (cuda is in /usr/local/cuda
and sdk is in /usr/local/cuda/sdk)
4. go to /usr/local/cudpp/common/ and type make and then enter l... | 1.0 | cudpp1.1.1 with cuda3.1 on ubuntu9.10 ../cudpp/make takes a long long time - ```
What steps will reproduce the problem?
1.download and install cuda 3.1 (first the driver-> toolkit ->sdk) on ubuntu
9.10
2.compile sdk
3.download cudpp1.1.1 and place in /usr/local/cudpp (cuda is in /usr/local/cuda
and sdk is in /usr/loc... | defect | with on cudpp make takes a long long time what steps will reproduce the problem download and install cuda first the driver toolkit sdk on ubuntu compile sdk download and place in usr local cudpp cuda is in usr local cuda and sdk is in usr local cuda sdk go to ... | 1 |
20,188 | 3,314,629,930 | IssuesEvent | 2015-11-06 06:55:02 | yinheli/lightweight-java-profiler | https://api.github.com/repos/yinheli/lightweight-java-profiler | closed | Wrong stacktraces are returned for complex interface structures. | auto-migrated Priority-Medium Type-Defect | ```
What steps will reproduce the problem?
1. In globals.h, change the kNumInterrupts to 30, and the kMaxStackTraces to
30000 (to make sure there will be enough space to record the whole execution)
2. Run the attached java file
3. Look for all List1.writeInt stack traces. One of those comes from a
computeList2 metho... | 1.0 | Wrong stacktraces are returned for complex interface structures. - ```
What steps will reproduce the problem?
1. In globals.h, change the kNumInterrupts to 30, and the kMaxStackTraces to
30000 (to make sure there will be enough space to record the whole execution)
2. Run the attached java file
3. Look for all List1.w... | defect | wrong stacktraces are returned for complex interface structures what steps will reproduce the problem in globals h change the knuminterrupts to and the kmaxstacktraces to to make sure there will be enough space to record the whole execution run the attached java file look for all writeint s... | 1 |
330,533 | 10,043,918,741 | IssuesEvent | 2019-07-19 08:45:46 | OpenNebula/one | https://api.github.com/repos/OpenNebula/one | opened | Add new command for create/recreate FTS index for VM searching | Category: CLI Priority: Normal Status: Accepted Type: Feature | **Description**
It will be useful to have a command (e.g `onedb recreate-index`) for create/recreate the FTS index either for maintenance proposes or in case a DB that didn't support this feature get updated and start to support it.
**Use case**
- Facilitate DB maintenance task.
- Help to add the index in case... | 1.0 | Add new command for create/recreate FTS index for VM searching - **Description**
It will be useful to have a command (e.g `onedb recreate-index`) for create/recreate the FTS index either for maintenance proposes or in case a DB that didn't support this feature get updated and start to support it.
**Use case**
- ... | non_defect | add new command for create recreate fts index for vm searching description it will be useful to have a command e g onedb recreate index for create recreate the fts index either for maintenance proposes or in case a db that didn t support this feature get updated and start to support it use case ... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.