Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 757 | labels stringlengths 4 664 | body stringlengths 3 261k | index stringclasses 10
values | text_combine stringlengths 96 261k | label stringclasses 2
values | text stringlengths 96 232k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
41,771 | 2,869,080,369 | IssuesEvent | 2015-06-05 23:10:30 | dart-lang/polymer-dart | https://api.github.com/repos/dart-lang/polymer-dart | closed | Polymer test_custom_event_test fails on Safari 6.2. | bug duplicate Priority-Medium | <a href="https://github.com/whesse"><img src="https://avatars.githubusercontent.com/u/4905639?v=3" align="left" width="96" height="96"hspace="10"></img></a> **Issue by [whesse](https://github.com/whesse)**
_Originally opened as dart-lang/sdk#21425_
----
The test pkg/polymer/test/custom_event_test fails on Safari 6.2 ... | 1.0 | Polymer test_custom_event_test fails on Safari 6.2. - <a href="https://github.com/whesse"><img src="https://avatars.githubusercontent.com/u/4905639?v=3" align="left" width="96" height="96"hspace="10"></img></a> **Issue by [whesse](https://github.com/whesse)**
_Originally opened as dart-lang/sdk#21425_
----
The test p... | non_defect | polymer test custom event test fails on safari issue by originally opened as dart lang sdk the test pkg polymer test custom event test fails on safari on macos error is type window onerror nbsp nbsp nbsp nbsp nbsp nbsp nbsp nbsp nbsp nbsp nbsp nbsp nbsp nbsp value... | 0 |
2,111 | 2,603,976,485 | IssuesEvent | 2015-02-24 19:01:37 | chrsmith/nishazi6 | https://api.github.com/repos/chrsmith/nishazi6 | opened | 沈阳龟头上肉芽 | auto-migrated Priority-Medium Type-Defect | ```
沈阳龟头上肉芽〓沈陽軍區政治部醫院性病〓TEL:024-31023308��
�成立于1946年,68年專注于性傳播疾病的研究和治療。位于沈�
��市沈河區二緯路32號。是一所與新中國同建立共輝煌的歷史�
��久、設備精良、技術權威、專家云集,是預防、保健、醫療
、科研康復為一體的綜合性醫院。是國家首批公立甲等部隊��
�院、全國首批醫療規范定點單位,是第四軍醫大學、東南大�
��等知名高等院校的教學醫院。曾被中國人民解放軍空軍后勤
部衛生部評為衛生工作先進單位,先后兩次榮立集體二等功��
�
```
-----
Original issue reported on code.google.com by `q964105.... | 1.0 | 沈阳龟头上肉芽 - ```
沈阳龟头上肉芽〓沈陽軍區政治部醫院性病〓TEL:024-31023308��
�成立于1946年,68年專注于性傳播疾病的研究和治療。位于沈�
��市沈河區二緯路32號。是一所與新中國同建立共輝煌的歷史�
��久、設備精良、技術權威、專家云集,是預防、保健、醫療
、科研康復為一體的綜合性醫院。是國家首批公立甲等部隊��
�院、全國首批醫療規范定點單位,是第四軍醫大學、東南大�
��等知名高等院校的教學醫院。曾被中國人民解放軍空軍后勤
部衛生部評為衛生工作先進單位,先后兩次榮立集體二等功��
�
```
-----
Original issue reported on code.google.com by... | defect | 沈阳龟头上肉芽 沈阳龟头上肉芽〓沈陽軍區政治部醫院性病〓tel: �� � , 。位于沈� �� 。是一所與新中國同建立共輝煌的歷史� ��久、設備精良、技術權威、專家云集,是預防、保健、醫療 、科研康復為一體的綜合性醫院。是國家首批公立甲等部隊�� �院、全國首批醫療規范定點單位,是第四軍醫大學、東南大� ��等知名高等院校的教學醫院。曾被中國人民解放軍空軍后勤 部衛生部評為衛生工作先進單位,先后兩次榮立集體二等功�� � original issue reported on code google com by gmail com on jun at | 1 |
52,914 | 13,772,794,781 | IssuesEvent | 2020-10-08 01:39:32 | raindigi/reaction | https://api.github.com/repos/raindigi/reaction | opened | CVE-2019-20922 (High) detected in handlebars-4.1.0.tgz | security vulnerability | ## CVE-2019-20922 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.0.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates ... | True | CVE-2019-20922 (High) detected in handlebars-4.1.0.tgz - ## CVE-2019-20922 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.0.tgz</b></p></summary>
<p>Handlebars provides... | non_defect | cve high detected in handlebars tgz cve high severity vulnerability vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file reaction pa... | 0 |
77,353 | 26,945,713,940 | IssuesEvent | 2023-02-08 07:54:00 | vector-im/element-x-ios | https://api.github.com/repos/vector-im/element-x-ios | closed | Room avatars disappear in room list | T-Defect | **Describe the bug**
Sometimes all avatars on the room list and the fallback (coloured avatar with a letter in it) appear instead
**To Reproduce**
I haven't been able to pin-point steps to reproduce, but it seems to happen when going back from the chat view to the room list, and there's a flash on the correct ... | 1.0 | Room avatars disappear in room list - **Describe the bug**
Sometimes all avatars on the room list and the fallback (coloured avatar with a letter in it) appear instead
**To Reproduce**
I haven't been able to pin-point steps to reproduce, but it seems to happen when going back from the chat view to the room lis... | defect | room avatars disappear in room list describe the bug sometimes all avatars on the room list and the fallback coloured avatar with a letter in it appear instead to reproduce i haven t been able to pin point steps to reproduce but it seems to happen when going back from the chat view to the room lis... | 1 |
24,352 | 3,968,652,667 | IssuesEvent | 2016-05-03 20:26:09 | lester88a/snova | https://api.github.com/repos/lester88a/snova | closed | 终于部署成功,但访问FB速度好慢。。。。 | auto-migrated Priority-Medium Type-Defect | ```
终于部署成功,但访问FB速度好慢。。。。是怎么个情况呢?
```
Original issue reported on code.google.com by `dover...@gmail.com` on 29 Jan 2014 at 9:25 | 1.0 | 终于部署成功,但访问FB速度好慢。。。。 - ```
终于部署成功,但访问FB速度好慢。。。。是怎么个情况呢?
```
Original issue reported on code.google.com by `dover...@gmail.com` on 29 Jan 2014 at 9:25 | defect | 终于部署成功,但访问fb速度好慢。。。。 终于部署成功,但访问fb速度好慢。。。。是怎么个情况呢? original issue reported on code google com by dover gmail com on jan at | 1 |
714,217 | 24,554,788,299 | IssuesEvent | 2022-10-12 15:05:03 | ooni/probe | https://api.github.com/repos/ooni/probe | opened | miniooni: add --remote=REMOTE functionality | enhancement priority/medium research prototype methodology ooni/probe-engine | This functionality has been discussed with @ainghazal for quite some time now. The general idea is that we are able to capture all the traffic generated by a miniooni instance and "remote" the traffic to a remote endpoint using a transport.
The main use case for this functionality seems to run integration testing in... | 1.0 | miniooni: add --remote=REMOTE functionality - This functionality has been discussed with @ainghazal for quite some time now. The general idea is that we are able to capture all the traffic generated by a miniooni instance and "remote" the traffic to a remote endpoint using a transport.
The main use case for this fun... | non_defect | miniooni add remote remote functionality this functionality has been discussed with ainghazal for quite some time now the general idea is that we are able to capture all the traffic generated by a miniooni instance and remote the traffic to a remote endpoint using a transport the main use case for this fun... | 0 |
97,650 | 12,248,940,647 | IssuesEvent | 2020-05-05 18:22:25 | project-koku/koku-ui | https://api.github.com/repos/project-koku/koku-ui | closed | RFE for UI HCCM/AWS heath check/current status | GA design enhancement | We should consider adding a monitor for Cost and sources (AWS, Azure, OCP) so we can see current status, basically being able to quickly tell if cost management has stale data and what time stamp the last data was collected on. | 1.0 | RFE for UI HCCM/AWS heath check/current status - We should consider adding a monitor for Cost and sources (AWS, Azure, OCP) so we can see current status, basically being able to quickly tell if cost management has stale data and what time stamp the last data was collected on. | non_defect | rfe for ui hccm aws heath check current status we should consider adding a monitor for cost and sources aws azure ocp so we can see current status basically being able to quickly tell if cost management has stale data and what time stamp the last data was collected on | 0 |
18,681 | 3,080,680,543 | IssuesEvent | 2015-08-22 00:32:16 | jameslh/pagedown | https://api.github.com/repos/jameslh/pagedown | closed | Enable Superscripts and subscripts as defined in Pandoc Markdown extension | auto-migrated Priority-Medium Type-Defect | ```
What steps will reproduce the problem?
1. In text editor, use ~word~ ( ^word^ ) to mark chars as sub or superscript.
2. Check the HTML preview
What is the expected output? What do you see instead?
If the Pandoc Extensions: superscript and subscript (see [1]) were supported,
it would be easy to markup sup and supe... | 1.0 | Enable Superscripts and subscripts as defined in Pandoc Markdown extension - ```
What steps will reproduce the problem?
1. In text editor, use ~word~ ( ^word^ ) to mark chars as sub or superscript.
2. Check the HTML preview
What is the expected output? What do you see instead?
If the Pandoc Extensions: superscript and... | defect | enable superscripts and subscripts as defined in pandoc markdown extension what steps will reproduce the problem in text editor use word word to mark chars as sub or superscript check the html preview what is the expected output what do you see instead if the pandoc extensions superscript and... | 1 |
46,508 | 2,958,386,437 | IssuesEvent | 2015-07-08 21:07:27 | evil-mad/EggBot | https://api.github.com/repos/evil-mad/EggBot | closed | Add unicode support | enhancement priority-high | Currently, reportedly, unicode characters in the text of the document or layer names can cause an error.
See here for possible solutions:
http://stackoverflow.com/questions/2365411/python-convert-unicode-to-ascii-without-errors | 1.0 | Add unicode support - Currently, reportedly, unicode characters in the text of the document or layer names can cause an error.
See here for possible solutions:
http://stackoverflow.com/questions/2365411/python-convert-unicode-to-ascii-without-errors | non_defect | add unicode support currently reportedly unicode characters in the text of the document or layer names can cause an error see here for possible solutions | 0 |
9,709 | 2,615,166,229 | IssuesEvent | 2015-03-01 06:46:42 | chrsmith/reaver-wps | https://api.github.com/repos/chrsmith/reaver-wps | opened | Found PIN but bad password | auto-migrated Priority-Triage Type-Defect | ```
0. What version of Reaver are you using? (Only defects against the latest
version will be considered.)
1.4
1. What operating system are you using (Linux is the only supported OS)?
backtrack 5 r3
2. Is your wireless card in monitor mode (yes/no)?
yes
3. What is the signal strength of the Access Point you are... | 1.0 | Found PIN but bad password - ```
0. What version of Reaver are you using? (Only defects against the latest
version will be considered.)
1.4
1. What operating system are you using (Linux is the only supported OS)?
backtrack 5 r3
2. Is your wireless card in monitor mode (yes/no)?
yes
3. What is the signal strengt... | defect | found pin but bad password what version of reaver are you using only defects against the latest version will be considered what operating system are you using linux is the only supported os backtrack is your wireless card in monitor mode yes no yes what is the signal strength... | 1 |
7,124 | 9,416,740,834 | IssuesEvent | 2019-04-10 15:15:14 | elementor/elementor | https://api.github.com/repos/elementor/elementor | closed | Plugin Update Needed to Correct URL requests (Elementor) | compatibility | This plugin is inserting outdated URL’s into the page, for example, this one;
`<svg xmlns="http://www.w3.org/2000/svg" viewBox="0 0 283.5 19.6" preserveAspectRatio="none">`
w3 website now uses HTTPS and the developers of Elementor need to update ALL their coding that uses outdated HTTP protocols to use HTTPS.
... | True | Plugin Update Needed to Correct URL requests (Elementor) - This plugin is inserting outdated URL’s into the page, for example, this one;
`<svg xmlns="http://www.w3.org/2000/svg" viewBox="0 0 283.5 19.6" preserveAspectRatio="none">`
w3 website now uses HTTPS and the developers of Elementor need to update ALL their... | non_defect | plugin update needed to correct url requests elementor this plugin is inserting outdated url’s into the page for example this one website now uses https and the developers of elementor need to update all their coding that uses outdated http protocols to use https this would also correct issues r... | 0 |
196,878 | 22,571,814,178 | IssuesEvent | 2022-06-28 01:25:46 | ChoeMinji/react-17.0.2 | https://api.github.com/repos/ChoeMinji/react-17.0.2 | opened | CVE-2021-42740 (High) detected in multiple libraries | security vulnerability | ## CVE-2021-42740 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>shell-quote-1.7.2.tgz</b>, <b>shell-quote-1.7.1.tgz</b>, <b>shell-quote-1.6.1.tgz</b></p></summary>
<p>
<details><su... | True | CVE-2021-42740 (High) detected in multiple libraries - ## CVE-2021-42740 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>shell-quote-1.7.2.tgz</b>, <b>shell-quote-1.7.1.tgz</b>, <b>sh... | non_defect | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries shell quote tgz shell quote tgz shell quote tgz shell quote tgz quote and parse shell commands library home page a href dependency hierarchy rea... | 0 |
12,228 | 2,685,518,402 | IssuesEvent | 2015-03-30 02:05:15 | IssueMigrationTest/Test5 | https://api.github.com/repos/IssueMigrationTest/Test5 | closed | annotations missing last character of last line | auto-migrated Priority-Medium Type-Defect | **Issue by willvar...@gmail.com**
_30 Sep 2011 at 12:53 GMT_
_Originally opened on Google Code_
----
```
What steps will reproduce the problem?
1. annotate anything where the last line is not empty
2. observe the last character is missing
Fix:
annotate.py, paste function, change this line:
line = source[expr.line... | 1.0 | annotations missing last character of last line - **Issue by willvar...@gmail.com**
_30 Sep 2011 at 12:53 GMT_
_Originally opened on Google Code_
----
```
What steps will reproduce the problem?
1. annotate anything where the last line is not empty
2. observe the last character is missing
Fix:
annotate.py, paste fu... | defect | annotations missing last character of last line issue by willvar gmail com sep at gmt originally opened on google code what steps will reproduce the problem annotate anything where the last line is not empty observe the last character is missing fix annotate py paste function... | 1 |
5,201 | 2,610,183,070 | IssuesEvent | 2015-02-26 18:58:18 | chrsmith/quchuseban | https://api.github.com/repos/chrsmith/quchuseban | opened | 纠结怎么样才能去掉色斑 | auto-migrated Priority-Medium Type-Defect | ```
《摘要》
想着曾经的画面,有多么美好,现在的疼痛,就有多么悲殇��
�不是我多情,只是我遇见了你,你就是我的桃花劫,不是我�
��情,只是我爱上了你,你就是我的鸳鸯梦,忆起那份约定,
在天愿作比翼鸟,在地愿为连理枝。泪早就流空了,只是心��
�一阵阵的绞痛,绝望的痛彻着,犹如深夜里大海的暗涌,歇�
��底里的咆哮着,只因,如今的我,成了断翅的鸟儿,成了无
根的浮萍。如果没有了色斑,我们是否会一起走进婚姻的殿��
�!怎么样才能去掉色斑,
《客户案例》
一直认为美丽不属于我,没想到去除色斑之后,我也来��
�个大变身。我从小就长了色斑,与遗传因素无关吧应该,父�
��的皮肤都很好,我就搞不懂自己这张脸了,随着年龄的增长
,... | 1.0 | 纠结怎么样才能去掉色斑 - ```
《摘要》
想着曾经的画面,有多么美好,现在的疼痛,就有多么悲殇��
�不是我多情,只是我遇见了你,你就是我的桃花劫,不是我�
��情,只是我爱上了你,你就是我的鸳鸯梦,忆起那份约定,
在天愿作比翼鸟,在地愿为连理枝。泪早就流空了,只是心��
�一阵阵的绞痛,绝望的痛彻着,犹如深夜里大海的暗涌,歇�
��底里的咆哮着,只因,如今的我,成了断翅的鸟儿,成了无
根的浮萍。如果没有了色斑,我们是否会一起走进婚姻的殿��
�!怎么样才能去掉色斑,
《客户案例》
一直认为美丽不属于我,没想到去除色斑之后,我也来��
�个大变身。我从小就长了色斑,与遗传因素无关吧应该,父�
��的皮肤都很好,我就搞不懂自... | defect | 纠结怎么样才能去掉色斑 《摘要》 想着曾经的画面,有多么美好,现在的疼痛,就有多么悲殇�� �不是我多情,只是我遇见了你,你就是我的桃花劫,不是我� ��情,只是我爱上了你,你就是我的鸳鸯梦,忆起那份约定, 在天愿作比翼鸟,在地愿为连理枝。泪早就流空了,只是心�� �一阵阵的绞痛,绝望的痛彻着,犹如深夜里大海的暗涌,歇� ��底里的咆哮着,只因,如今的我,成了断翅的鸟儿,成了无 根的浮萍。如果没有了色斑,我们是否会一起走进婚姻的殿�� �!怎么样才能去掉色斑, 《客户案例》 一直认为美丽不属于我,没想到去除色斑之后,我也来�� �个大变身。我从小就长了色斑,与遗传因素无关吧应该,父� ��的皮肤都很好,我就搞不懂自... | 1 |
37,041 | 15,159,226,749 | IssuesEvent | 2021-02-12 03:34:36 | ruma/ruma | https://api.github.com/repos/ruma/ruma | closed | identity-service: Add autodiscovery endpoint | crate/ruma-identity-service-api help wanted | Endpoint: `GET /_matrix/identity/v2`
Docs: https://matrix.org/docs/spec/identity_service/r0.3.0#get-matrix-identity-v2
[Suggested] Module name: `status::v2`? | 1.0 | identity-service: Add autodiscovery endpoint - Endpoint: `GET /_matrix/identity/v2`
Docs: https://matrix.org/docs/spec/identity_service/r0.3.0#get-matrix-identity-v2
[Suggested] Module name: `status::v2`? | non_defect | identity service add autodiscovery endpoint endpoint get matrix identity docs module name status | 0 |
95,104 | 16,068,474,066 | IssuesEvent | 2021-04-24 00:45:02 | snowflakedb/snowflake-hive-metastore-connector | https://api.github.com/repos/snowflakedb/snowflake-hive-metastore-connector | opened | CVE-2019-10202 (High) detected in jackson-databind-2.6.5.jar, jackson-mapper-asl-1.9.13.jar | security vulnerability | ## CVE-2019-10202 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.6.5.jar</b>, <b>jackson-mapper-asl-1.9.13.jar</b></p></summary>
<p>
<details><summary><b>jackson-... | True | CVE-2019-10202 (High) detected in jackson-databind-2.6.5.jar, jackson-mapper-asl-1.9.13.jar - ## CVE-2019-10202 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.6.5.... | non_defect | cve high detected in jackson databind jar jackson mapper asl jar cve high severity vulnerability vulnerable libraries jackson databind jar jackson mapper asl jar jackson databind jar general data binding functionality for jackson works on core str... | 0 |
297,989 | 25,779,017,297 | IssuesEvent | 2022-12-09 14:24:59 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | closed | 🥐🥐 Flaky E2E Test Detected! secure-messaging-messages-faq.cypress.spec.js | MHV-Secure-Messaging e2e-flaky-test | Your test spec `src/applications/mhv/secure-messaging/tests/e2e/secure-messaging-messages-faq.cypress.spec.js`
has been disallowed from running on vets-website due to flakiness since 10/28/2022. Please make corrections to the test spec and run it through CI to have it re-enabled. | 1.0 | 🥐🥐 Flaky E2E Test Detected! secure-messaging-messages-faq.cypress.spec.js - Your test spec `src/applications/mhv/secure-messaging/tests/e2e/secure-messaging-messages-faq.cypress.spec.js`
has been disallowed from running on vets-website due to flakiness since 10/28/2022. Please make corrections to the test spec and r... | non_defect | 🥐🥐 flaky test detected secure messaging messages faq cypress spec js your test spec src applications mhv secure messaging tests secure messaging messages faq cypress spec js has been disallowed from running on vets website due to flakiness since please make corrections to the test spec and run it thr... | 0 |
94,992 | 19,636,225,354 | IssuesEvent | 2022-01-08 10:28:31 | harshagrawal523/Portfolyser | https://api.github.com/repos/harshagrawal523/Portfolyser | closed | Authenticate user while registering. | enhancement CodePeak Easy | Right now, when a new account is made using email login, the user is redirected to the login page.
We should authenticate the user even if they are registering a new account. | 1.0 | Authenticate user while registering. - Right now, when a new account is made using email login, the user is redirected to the login page.
We should authenticate the user even if they are registering a new account. | non_defect | authenticate user while registering right now when a new account is made using email login the user is redirected to the login page we should authenticate the user even if they are registering a new account | 0 |
43,122 | 11,490,232,892 | IssuesEvent | 2020-02-11 16:44:53 | mozilla/blurts-server | https://api.github.com/repos/mozilla/blurts-server | closed | Broken image displayed for the account avatar if the user deletes the Account picture | defect feature-fxa | [Affected versions]:
- Firefox 65.0.1
[Affected Platforms]:
- Windows 10 x64
- macOS 10.13
- Ubuntu 18.04 x64
[Steps to reproduce]:
1. Navigate to http://stage.firefoxmonitor.nonprod.cloudops.mozgcp.net and Sign in with a valid account.
2. Go to https://stable.dev.lcip.org/settings and change the default "A... | 1.0 | Broken image displayed for the account avatar if the user deletes the Account picture - [Affected versions]:
- Firefox 65.0.1
[Affected Platforms]:
- Windows 10 x64
- macOS 10.13
- Ubuntu 18.04 x64
[Steps to reproduce]:
1. Navigate to http://stage.firefoxmonitor.nonprod.cloudops.mozgcp.net and Sign in with ... | defect | broken image displayed for the account avatar if the user deletes the account picture firefox windows macos ubuntu navigate to and sign in with a valid account go to and change the default account picture to any other one click on the change button... | 1 |
20,334 | 3,343,341,313 | IssuesEvent | 2015-11-15 12:19:12 | bridgedotnet/Bridge | https://api.github.com/repos/bridgedotnet/Bridge | closed | Missed Array's .CopyTo(). There are two overloads | defect | http://forums.bridge.net/forum/general/feature-requests/727
`public void CopyTo(Array array, int index)`
`public void CopyTo(Array array, long index)`
A related Bridge v2 [issue](https://github.com/bridgedotnet/Bridge2/issues/38). | 1.0 | Missed Array's .CopyTo(). There are two overloads - http://forums.bridge.net/forum/general/feature-requests/727
`public void CopyTo(Array array, int index)`
`public void CopyTo(Array array, long index)`
A related Bridge v2 [issue](https://github.com/bridgedotnet/Bridge2/issues/38). | defect | missed array s copyto there are two overloads public void copyto array array int index public void copyto array array long index a related bridge | 1 |
7,348 | 2,894,227,280 | IssuesEvent | 2015-06-15 22:11:47 | mouseas/steamSummerMinigame | https://api.github.com/repos/mouseas/steamSummerMinigame | closed | Syntax error, script broken | needs testing | From Chrome console:
```
Syntax error @ 'Monster Minigame AutoScript'!
##########################
JSHINT output:
script: (W033) Missing semicolon on line: 84 at character: 2
script: (W033) Missing semicolon on line: 103 at character: 10
script: (W033) Missing semicolon on line: 177 at character: 6
script: (W0... | 1.0 | Syntax error, script broken - From Chrome console:
```
Syntax error @ 'Monster Minigame AutoScript'!
##########################
JSHINT output:
script: (W033) Missing semicolon on line: 84 at character: 2
script: (W033) Missing semicolon on line: 103 at character: 10
script: (W033) Missing semicolon on line: 17... | non_defect | syntax error script broken from chrome console syntax error monster minigame autoscript jshint output script missing semicolon on line at character script missing semicolon on line at character script missing semicolon on line at character ... | 0 |
86,899 | 15,755,896,289 | IssuesEvent | 2021-03-31 02:34:29 | turkdevops/node | https://api.github.com/repos/turkdevops/node | opened | CVE-2015-1790 (Medium) detected in opensslOpenSSL_1_0_1i | security vulnerability | ## CVE-2015-1790 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opensslOpenSSL_1_0_1i</b></p></summary>
<p>
<p>TLS/SSL and crypto library</p>
<p>Library home page: <a href=https://g... | True | CVE-2015-1790 (Medium) detected in opensslOpenSSL_1_0_1i - ## CVE-2015-1790 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opensslOpenSSL_1_0_1i</b></p></summary>
<p>
<p>TLS/SSL and... | non_defect | cve medium detected in opensslopenssl cve medium severity vulnerability vulnerable library opensslopenssl tls ssl and crypto library library home page a href found in base branch archived io js vulnerable source files node deps openssl... | 0 |
27,651 | 5,073,293,233 | IssuesEvent | 2016-12-27 07:48:10 | TNGSB/eWallet | https://api.github.com/repos/TNGSB/eWallet | closed | e-Wallet_Merchant Portal (Voucher Used Details Report)_19122016 #153 | ABL Defect - High (Sev-2) Dev Environment | Test Description : To download the Voucher Used Details Report
Expected Result : 1. Succesfully download the report in PDF format
Actual Result : System displayed Bad Credentials page
Steps: 1. User to click Export as PDF link of the report from the page
Refer attachment for reference
[Defect_MerchantPortal_... | 1.0 | e-Wallet_Merchant Portal (Voucher Used Details Report)_19122016 #153 - Test Description : To download the Voucher Used Details Report
Expected Result : 1. Succesfully download the report in PDF format
Actual Result : System displayed Bad Credentials page
Steps: 1. User to click Export as PDF link of the report f... | defect | e wallet merchant portal voucher used details report test description to download the voucher used details report expected result succesfully download the report in pdf format actual result system displayed bad credentials page steps user to click export as pdf link of the report from the p... | 1 |
625,812 | 19,766,576,233 | IssuesEvent | 2022-01-17 03:38:20 | aitos-io/BoAT-X-Framework | https://api.github.com/repos/aitos-io/BoAT-X-Framework | closed | Pointer error in web3 function | bug Severity/major Priority/P1 | web3Result is a pointer to BOAT_RESULT, and need to determine if the input pointer is null, not if the value is null.
```
BOAT_RESULT *web3Result
if(*web3Result != NULL){
*web3Result = result;
}
``` | 1.0 | Pointer error in web3 function - web3Result is a pointer to BOAT_RESULT, and need to determine if the input pointer is null, not if the value is null.
```
BOAT_RESULT *web3Result
if(*web3Result != NULL){
*web3Result = result;
}
``` | non_defect | pointer error in function is a pointer to boat result and need to determine if the input pointer is null not if the value is null boat result if null result | 0 |
19,432 | 3,202,767,025 | IssuesEvent | 2015-10-02 15:34:09 | JPaulMora/Pyrit | https://api.github.com/repos/JPaulMora/Pyrit | closed | pyrit server | auto-migrated Priority-Medium Type-Defect | ```
hi i have problems with Pyrite server
get it when I run Pyrite benchmark on the client
detested is what gets on Pyrite server
plis help!!!
Please provide any additional information below.
Serving 1 active clients; 0 PMKs/s; 0.0 TTS Exception in thread Thread-20:
Traceback (most recent call last):
File "/usr/li... | 1.0 | pyrit server - ```
hi i have problems with Pyrite server
get it when I run Pyrite benchmark on the client
detested is what gets on Pyrite server
plis help!!!
Please provide any additional information below.
Serving 1 active clients; 0 PMKs/s; 0.0 TTS Exception in thread Thread-20:
Traceback (most recent call last):
... | defect | pyrit server hi i have problems with pyrite server get it when i run pyrite benchmark on the client detested is what gets on pyrite server plis help please provide any additional information below serving active clients pmks s tts exception in thread thread traceback most recent call last ... | 1 |
720,539 | 24,796,394,785 | IssuesEvent | 2022-10-24 17:39:32 | AmplifyCreations/AmplifyShaderEditor-Feedback | https://api.github.com/repos/AmplifyCreations/AmplifyShaderEditor-Feedback | closed | HDRP 12 Bug - undeclared identifier 'GetMaterialDebugColor' | bug highest priority | Repo: Enter a prefab and disable the lighting
Unity 2021.3.11
HDRP 12.1.7
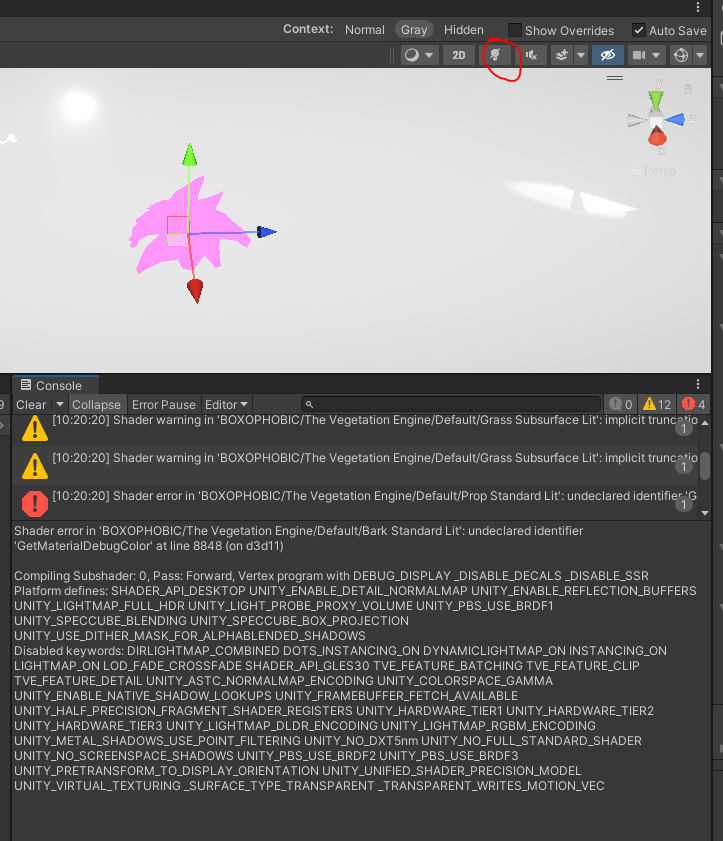
| 1.0 | HDRP 12 Bug - undeclared identifier 'GetMaterialDebugColor' - Repo: Enter a prefab and disable the lighting
Unity 2021.3.11
HDRP 12.1.7
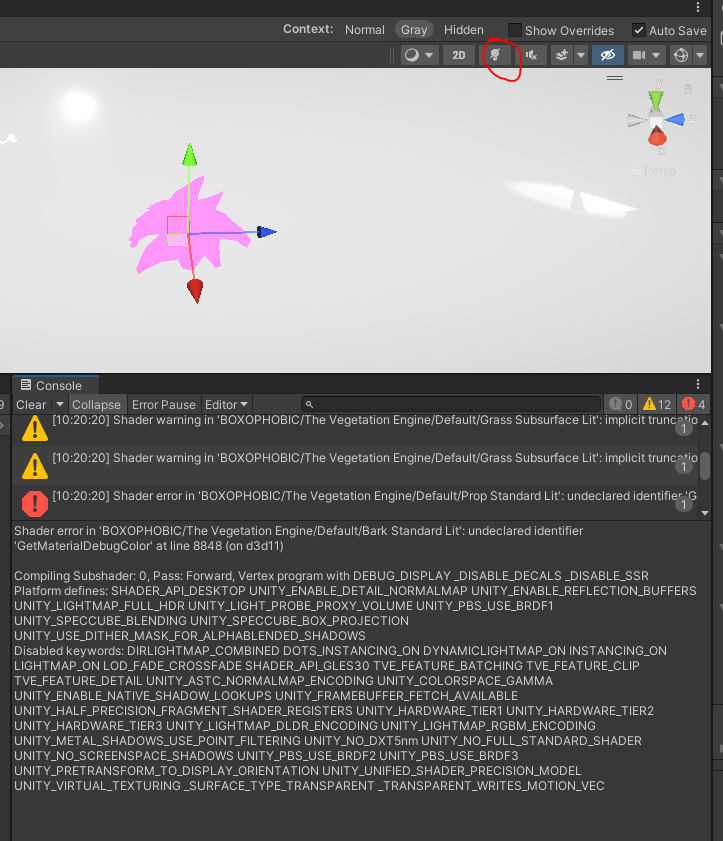
| non_defect | hdrp bug undeclared identifier getmaterialdebugcolor repo enter a prefab and disable the lighting unity hdrp | 0 |
128,002 | 5,042,393,872 | IssuesEvent | 2016-12-19 13:51:31 | pombase/curation | https://api.github.com/repos/pombase/curation | closed | cdc15 -> cdc7 | high priority |
There are a couple of cdc7alleles on the cdc15 gene page (looks like copy paste and not editing allele)
Also, one of these is
mitotic G2/M transition delay
I suspect this should be
inviable binucleate aseptate cell with mitotic cell cycle arrest in G2 before cell separation
which is when there is a G2 a... | 1.0 | cdc15 -> cdc7 -
There are a couple of cdc7alleles on the cdc15 gene page (looks like copy paste and not editing allele)
Also, one of these is
mitotic G2/M transition delay
I suspect this should be
inviable binucleate aseptate cell with mitotic cell cycle arrest in G2 before cell separation
which is when... | non_defect | there are a couple of on the gene page looks like copy paste and not editing allele also one of these is mitotic m transition delay i suspect this should be inviable binucleate aseptate cell with mitotic cell cycle arrest in before cell separation which is when there is a arrest in... | 0 |
71,405 | 23,612,103,678 | IssuesEvent | 2022-08-24 13:13:43 | vector-im/element-android | https://api.github.com/repos/vector-im/element-android | closed | [bug] not possible to verify Android Version | T-Defect | ### Steps to reproduce
### Steps to reproduce
1. for weeks i enabled a other Beta-Feature at Linux Client Element. works very well
2. then i enabled this other Beta-Feature at Android Client Element. not works. it waits for server response for days, and it still wait at the moment.
3. i disabled the beta at lin... | 1.0 | [bug] not possible to verify Android Version - ### Steps to reproduce
### Steps to reproduce
1. for weeks i enabled a other Beta-Feature at Linux Client Element. works very well
2. then i enabled this other Beta-Feature at Android Client Element. not works. it waits for server response for days, and it still wai... | defect | not possible to verify android version steps to reproduce steps to reproduce for weeks i enabled a other beta feature at linux client element works very well then i enabled this other beta feature at android client element not works it waits for server response for days and it still wait at... | 1 |
80,906 | 30,592,723,879 | IssuesEvent | 2023-07-21 18:35:41 | DependencyTrack/dependency-track | https://api.github.com/repos/DependencyTrack/dependency-track | closed | Update Docker image to latest debian stable release | defect | ### Current Behavior
When pulling docker bundled image, I noticed the base image is outdated a little bit. Recommend updating to the latest stable docker image.
Additionally, we should change the Dependabot schedule for docker to daily instead of weekly, to keep track of new updates for containers.
https://hub.... | 1.0 | Update Docker image to latest debian stable release - ### Current Behavior
When pulling docker bundled image, I noticed the base image is outdated a little bit. Recommend updating to the latest stable docker image.
Additionally, we should change the Dependabot schedule for docker to daily instead of weekly, to k... | defect | update docker image to latest debian stable release current behavior when pulling docker bundled image i noticed the base image is outdated a little bit recommend updating to the latest stable docker image additionally we should change the dependabot schedule for docker to daily instead of weekly to k... | 1 |
721,706 | 24,835,411,627 | IssuesEvent | 2022-10-26 08:27:41 | authzed/spicedb | https://api.github.com/repos/authzed/spicedb | closed | Investigate eliding updates of namespaces unchanged in schema write | priority/4 maybe area/perf area/api v1 | If a schema is written with namespaces that have not changed at all, investigate whether they need to be written
This can occur if the *same* schema is written by tooling | 1.0 | Investigate eliding updates of namespaces unchanged in schema write - If a schema is written with namespaces that have not changed at all, investigate whether they need to be written
This can occur if the *same* schema is written by tooling | non_defect | investigate eliding updates of namespaces unchanged in schema write if a schema is written with namespaces that have not changed at all investigate whether they need to be written this can occur if the same schema is written by tooling | 0 |
707,576 | 24,310,118,433 | IssuesEvent | 2022-09-29 21:19:35 | o3de/o3de | https://api.github.com/repos/o3de/o3de | closed | Landscape Canvas: Duplicated Landscape Canvas nodes have no attached components, are created outside of the LC parent hierarchy, and are not deleted upon node removal | kind/bug sig/content triage/accepted priority/critical feature/vegetation | **Describe the bug**
Duplicated Landscape Canvas nodes have no attached components, are created outside of the LC parent hierarchy, and are not deleted upon node removal
**Steps to reproduce**
1. Launch the Editor with the AutomatedTesting project.
2. Open Landscape Canvas (Tools > Landscape Canvas).
3. Drag a n... | 1.0 | Landscape Canvas: Duplicated Landscape Canvas nodes have no attached components, are created outside of the LC parent hierarchy, and are not deleted upon node removal - **Describe the bug**
Duplicated Landscape Canvas nodes have no attached components, are created outside of the LC parent hierarchy, and are not delete... | non_defect | landscape canvas duplicated landscape canvas nodes have no attached components are created outside of the lc parent hierarchy and are not deleted upon node removal describe the bug duplicated landscape canvas nodes have no attached components are created outside of the lc parent hierarchy and are not delete... | 0 |
71,785 | 23,802,722,956 | IssuesEvent | 2022-09-03 14:57:05 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | opened | QR codes for app download doesn't look nice in the dark theme | T-Defect | ### Steps to reproduce
1. Start out using Element Web
2. Use the dark theme
3. Click on “Download app”, and see the QR codes
### Outcome
#### What did you expect?
The QR codes should be inverted, or have a padding around it to make it look nice, though technically it is still scannable
#### What happened inste... | 1.0 | QR codes for app download doesn't look nice in the dark theme - ### Steps to reproduce
1. Start out using Element Web
2. Use the dark theme
3. Click on “Download app”, and see the QR codes
### Outcome
#### What did you expect?
The QR codes should be inverted, or have a padding around it to make it look nice, thou... | defect | qr codes for app download doesn t look nice in the dark theme steps to reproduce start out using element web use the dark theme click on “download app” and see the qr codes outcome what did you expect the qr codes should be inverted or have a padding around it to make it look nice thou... | 1 |
101,178 | 11,219,830,535 | IssuesEvent | 2020-01-07 14:40:53 | Maproom/qmapshack | https://api.github.com/repos/Maproom/qmapshack | closed | Missing SQLITE files mentioned in msvc_64/copyfiles.bat (Windows version) | bug documentation | **Describe the bug**
In the `msvc_64/copyfiles.bat` section 2.2.10 (sqlite) the 2 files
* `sqldiff.exe`
* `sqlite3_analyzer.exe`
should be copied. These files don't exist (are not downloaded from somewhere) when following the Windows installation instructions in the Wiki pages `BuildWindowsVisualStudio`and `Build... | 1.0 | Missing SQLITE files mentioned in msvc_64/copyfiles.bat (Windows version) - **Describe the bug**
In the `msvc_64/copyfiles.bat` section 2.2.10 (sqlite) the 2 files
* `sqldiff.exe`
* `sqlite3_analyzer.exe`
should be copied. These files don't exist (are not downloaded from somewhere) when following the Windows inst... | non_defect | missing sqlite files mentioned in msvc copyfiles bat windows version describe the bug in the msvc copyfiles bat section sqlite the files sqldiff exe analyzer exe should be copied these files don t exist are not downloaded from somewhere when following the windows installation ... | 0 |
90,862 | 15,856,291,535 | IssuesEvent | 2021-04-08 01:59:55 | tongni1975/containers-may19-2020-MyWork | https://api.github.com/repos/tongni1975/containers-may19-2020-MyWork | opened | CVE-2020-11023 (Medium) detected in jquery-2.1.4.min.js, jquery-1.7.1.min.js | security vulnerability | ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-2.1.4.min.js</b>, <b>jquery-1.7.1.min.js</b></p></summary>
<p>
<details><summary><b>jquery-2.1.4.min.js</b>... | True | CVE-2020-11023 (Medium) detected in jquery-2.1.4.min.js, jquery-1.7.1.min.js - ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-2.1.4.min.js</b>, <b>jquery-1... | non_defect | cve medium detected in jquery min js jquery min js cve medium severity vulnerability vulnerable libraries jquery min js jquery min js jquery min js javascript library for dom operations library home page a href path to dependency file cont... | 0 |
22,306 | 3,626,937,755 | IssuesEvent | 2016-02-10 04:53:01 | kronometrix/recording | https://api.github.com/repos/kronometrix/recording | closed | win32 nic detection mechanism optimizations | defect-high enhancement | It has been noticed that fetching NIC stats takes time up to 0.7seconds on some systems. For example a very simple procedure to simple fetch NIC stats calling a single perf class returns these timing results:
* Win32_PerfFormattedData_Tcpip_NetworkInterface
```
Realtek RTL8139C+ Fast Ethernet NIC
isatap.{F9A690... | 1.0 | win32 nic detection mechanism optimizations - It has been noticed that fetching NIC stats takes time up to 0.7seconds on some systems. For example a very simple procedure to simple fetch NIC stats calling a single perf class returns these timing results:
* Win32_PerfFormattedData_Tcpip_NetworkInterface
```
Realt... | defect | nic detection mechanism optimizations it has been noticed that fetching nic stats takes time up to on some systems for example a very simple procedure to simple fetch nic stats calling a single perf class returns these timing results perfformatteddata tcpip networkinterface realtek fast ethe... | 1 |
41,327 | 10,416,889,623 | IssuesEvent | 2019-09-14 17:07:52 | mozilla/blurts-server | https://api.github.com/repos/mozilla/blurts-server | closed | unsubscribe | Content :memo: feature-fxa :bust_in_silhouette: needs: PM needs: UX type: defect | When someone signs up with Firefox Account, they get a report email with blue text that says "If you no longer want Firefox Monitor alerts, unsubscribe." but they have no way to unsubscribe.
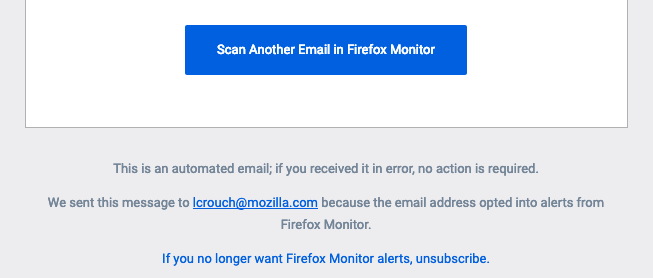
We should eithe... | 1.0 | unsubscribe - When someone signs up with Firefox Account, they get a report email with blue text that says "If you no longer want Firefox Monitor alerts, unsubscribe." but they have no way to unsubscribe.
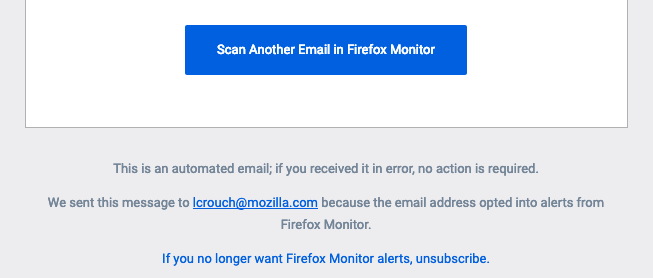
W... | defect | unsubscribe when someone signs up with firefox account they get a report email with blue text that says if you no longer want firefox monitor alerts unsubscribe but they have no way to unsubscribe we should either fix and link the recipient to that page or else restore the functionality to unsubs... | 1 |
77,152 | 7,567,127,444 | IssuesEvent | 2018-04-22 05:58:09 | intesar/Fx-Test-Data | https://api.github.com/repos/intesar/Fx-Test-Data | closed | Test-bvpoGI : enterprise_user_signup_invalid | Test-bvpoGI | Project : Test-bvpoGI
Job : Stg
Env : Stg
Region : FxLabs/US_WEST_1
Result : fail
Status Code : 503
Headers : {Cache-Control=[no-cache], Connection=[close], Content-Type=[text/html]}
Endpoint : http://stg1.fxlabs.io/api/v1/users/enterprise-sign-up
Request :
{
"name" : "fn1 ln",
"email" : ... | 1.0 | Test-bvpoGI : enterprise_user_signup_invalid - Project : Test-bvpoGI
Job : Stg
Env : Stg
Region : FxLabs/US_WEST_1
Result : fail
Status Code : 503
Headers : {Cache-Control=[no-cache], Connection=[close], Content-Type=[text/html]}
Endpoint : http://stg1.fxlabs.io/api/v1/users/enterprise-sign-up
R... | non_defect | test bvpogi enterprise user signup invalid project test bvpogi job stg env stg region fxlabs us west result fail status code headers cache control connection content type endpoint request name ln email test fxlabs io password ... | 0 |
58,362 | 16,504,676,441 | IssuesEvent | 2021-05-25 17:47:21 | matrix-org/synapse | https://api.github.com/repos/matrix-org/synapse | opened | Synapse workers Complement image results in flaky tests due to inconsistent worker process init | T-Defect X-Needs-Discussion | The worker-version of Synapse running in Complement (as described [here](https://github.com/matrix-org/synapse/blob/develop/docker/README-testing.md#testing-with-postgresql-and-single-or-multi-process-synapse)) currently uses `supervisord` as an init system to start all worker processes in the container.
This works,... | 1.0 | Synapse workers Complement image results in flaky tests due to inconsistent worker process init - The worker-version of Synapse running in Complement (as described [here](https://github.com/matrix-org/synapse/blob/develop/docker/README-testing.md#testing-with-postgresql-and-single-or-multi-process-synapse)) currently u... | defect | synapse workers complement image results in flaky tests due to inconsistent worker process init the worker version of synapse running in complement as described currently uses supervisord as an init system to start all worker processes in the container this works and eventually all processes start up how... | 1 |
67,695 | 14,886,277,616 | IssuesEvent | 2021-01-20 16:44:18 | kadirselcuk/angularjs-realworld-example-app | https://api.github.com/repos/kadirselcuk/angularjs-realworld-example-app | opened | WS-2018-0628 (Medium) detected in marked-0.3.19.js, marked-0.3.19.tgz | security vulnerability | ## WS-2018-0628 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>marked-0.3.19.js</b>, <b>marked-0.3.19.tgz</b></p></summary>
<p>
<details><summary><b>marked-0.3.19.js</b></p></summ... | True | WS-2018-0628 (Medium) detected in marked-0.3.19.js, marked-0.3.19.tgz - ## WS-2018-0628 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>marked-0.3.19.js</b>, <b>marked-0.3.19.tgz</b... | non_defect | ws medium detected in marked js marked tgz ws medium severity vulnerability vulnerable libraries marked js marked tgz marked js a markdown parser built for speed library home page a href path to dependency file angularjs realworld example ... | 0 |
44,210 | 12,043,546,829 | IssuesEvent | 2020-04-14 12:37:48 | primefaces/primeng | https://api.github.com/repos/primefaces/primeng | closed | Dropdown allows selecting disabled options | defect | Dropdown has a 'search' feature which allows one to find an item by typing its label. This feature works fine, but it seems to ignore the option's 'disabled' status.
Example:
1) A dropdown with options A, B, C. "B" is disabled;
2) Put focus on the dropdown (by mouse or keyboard);
3) Type "b" on the keyboard;
4) ... | 1.0 | Dropdown allows selecting disabled options - Dropdown has a 'search' feature which allows one to find an item by typing its label. This feature works fine, but it seems to ignore the option's 'disabled' status.
Example:
1) A dropdown with options A, B, C. "B" is disabled;
2) Put focus on the dropdown (by mouse or ... | defect | dropdown allows selecting disabled options dropdown has a search feature which allows one to find an item by typing its label this feature works fine but it seems to ignore the option s disabled status example a dropdown with options a b c b is disabled put focus on the dropdown by mouse or ... | 1 |
19,992 | 4,478,705,379 | IssuesEvent | 2016-08-27 05:35:03 | grandstaish/paperparcel | https://api.github.com/repos/grandstaish/paperparcel | closed | Add usage docs to the wiki | Documentation | Include how to parcel a kotlin object too, because it currently isn't called out. E.g.:
``` java
@PaperParcel
object State : PaperParcelable {
@JvmField val CREATOR = PaperParcelable.Creator(State::class.java)
}
``` | 1.0 | Add usage docs to the wiki - Include how to parcel a kotlin object too, because it currently isn't called out. E.g.:
``` java
@PaperParcel
object State : PaperParcelable {
@JvmField val CREATOR = PaperParcelable.Creator(State::class.java)
}
``` | non_defect | add usage docs to the wiki include how to parcel a kotlin object too because it currently isn t called out e g java paperparcel object state paperparcelable jvmfield val creator paperparcelable creator state class java | 0 |
24,575 | 11,046,997,126 | IssuesEvent | 2019-12-09 18:00:25 | LevyForchh/webdataconnector | https://api.github.com/repos/LevyForchh/webdataconnector | opened | WS-2019-0064 (High) detected in handlebars-4.0.5.min.js, handlebars-4.0.5.tgz | security vulnerability | ## WS-2019-0064 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>handlebars-4.0.5.min.js</b>, <b>handlebars-4.0.5.tgz</b></p></summary>
<p>
<details><summary><b>handlebars-4.0.5.min.j... | True | WS-2019-0064 (High) detected in handlebars-4.0.5.min.js, handlebars-4.0.5.tgz - ## WS-2019-0064 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>handlebars-4.0.5.min.js</b>, <b>handleb... | non_defect | ws high detected in handlebars min js handlebars tgz ws high severity vulnerability vulnerable libraries handlebars min js handlebars tgz handlebars min js handlebars provides the power necessary to let you build semantic templates effectively with... | 0 |
59,754 | 17,023,233,342 | IssuesEvent | 2021-07-03 00:59:00 | tomhughes/trac-tickets | https://api.github.com/repos/tomhughes/trac-tickets | closed | tah.openstreetmap.org handles empty parts wrong | Component: osmarender Priority: minor Resolution: fixed Type: defect | **[Submitted to the original trac issue database at 11.50am, Thursday, 10th April 2008]**
E.g. when you look at
http://tah.openstreetmap.org/MapOf/index.php?lat=51.1264&long=14.1847&z=14&h=1994&w=1389&format=png
there is an empty square part left of "Grodrebnitz".
This is an area, which is totally empty and drawn... | 1.0 | tah.openstreetmap.org handles empty parts wrong - **[Submitted to the original trac issue database at 11.50am, Thursday, 10th April 2008]**
E.g. when you look at
http://tah.openstreetmap.org/MapOf/index.php?lat=51.1264&long=14.1847&z=14&h=1994&w=1389&format=png
there is an empty square part left of "Grodrebnitz".
... | defect | tah openstreetmap org handles empty parts wrong e g when you look at there is an empty square part left of grodrebnitz this is an area which is totally empty and drawn totally white but the normal background is a light grey same for left beside schulzendorf solution for empty tiles us... | 1 |
9,609 | 2,615,163,625 | IssuesEvent | 2015-03-01 06:43:18 | chrsmith/reaver-wps | https://api.github.com/repos/chrsmith/reaver-wps | opened | WPS and WPS Pin | auto-migrated Priority-Triage Type-Defect | ```
Doing some Reaver (v.14) testing against my UK Virgin Media WPS enabled AP -
and have encountered some unexpected results.
Attachment 1 (available on request): wps_pin_en
Shows WPS and WPS PIN enabled on the AP.
Shows the WPS PIN.
Reaver input where I've "guessed" the PIN number.
Reaver output successfully retr... | 1.0 | WPS and WPS Pin - ```
Doing some Reaver (v.14) testing against my UK Virgin Media WPS enabled AP -
and have encountered some unexpected results.
Attachment 1 (available on request): wps_pin_en
Shows WPS and WPS PIN enabled on the AP.
Shows the WPS PIN.
Reaver input where I've "guessed" the PIN number.
Reaver output... | defect | wps and wps pin doing some reaver v testing against my uk virgin media wps enabled ap and have encountered some unexpected results attachment available on request wps pin en shows wps and wps pin enabled on the ap shows the wps pin reaver input where i ve guessed the pin number reaver output ... | 1 |
167,254 | 13,017,643,274 | IssuesEvent | 2020-07-26 13:33:41 | chaotic-aur/infra | https://api.github.com/repos/chaotic-aur/infra | closed | Matrix.org qt clients | pkg-request waiting-testing | `quaternion`, `quaternion-git`
`spectral-matrix`, `spectral-matrix-git`
`nheko`, `nheko-git`
`matrix-mirage`, `matrix-mirage-git` | 1.0 | Matrix.org qt clients - `quaternion`, `quaternion-git`
`spectral-matrix`, `spectral-matrix-git`
`nheko`, `nheko-git`
`matrix-mirage`, `matrix-mirage-git` | non_defect | matrix org qt clients quaternion quaternion git spectral matrix spectral matrix git nheko nheko git matrix mirage matrix mirage git | 0 |
15,110 | 11,355,647,318 | IssuesEvent | 2020-01-24 20:33:31 | enarx/enarx | https://api.github.com/repos/enarx/enarx | closed | Issue Templates | infrastructure | We need some decent issue templates. This is related, in part, to project infrastructure automation. | 1.0 | Issue Templates - We need some decent issue templates. This is related, in part, to project infrastructure automation. | non_defect | issue templates we need some decent issue templates this is related in part to project infrastructure automation | 0 |
30,928 | 6,359,320,092 | IssuesEvent | 2017-07-31 06:47:48 | ironjan/metal-only | https://api.github.com/repos/ironjan/metal-only | closed | UnknownHostException for 6 devices via PlayStore | defect duplicate | ```
org.springframework.web.client.ResourceAccessException:
at org.springframework.web.client.RestTemplate.doExecute (RestTemplate.java:491)
at org.springframework.web.client.RestTemplate.execute (RestTemplate.java:439)
at org.springframework.web.client.RestTemplate.exchange (RestTemplate.java:415)
at com... | 1.0 | UnknownHostException for 6 devices via PlayStore - ```
org.springframework.web.client.ResourceAccessException:
at org.springframework.web.client.RestTemplate.doExecute (RestTemplate.java:491)
at org.springframework.web.client.RestTemplate.execute (RestTemplate.java:439)
at org.springframework.web.client.Rest... | defect | unknownhostexception for devices via playstore org springframework web client resourceaccessexception at org springframework web client resttemplate doexecute resttemplate java at org springframework web client resttemplate execute resttemplate java at org springframework web client resttemp... | 1 |
228,084 | 25,154,674,536 | IssuesEvent | 2022-11-10 12:41:36 | vital-ws/npm-1 | https://api.github.com/repos/vital-ws/npm-1 | closed | express-4.0.0.tgz: 13 vulnerabilities (highest severity is: 7.5) - autoclosed | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>express-4.0.0.tgz</b></p></summary>
<p>Sinatra inspired web development framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/express/-/express-4.0.... | True | express-4.0.0.tgz: 13 vulnerabilities (highest severity is: 7.5) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>express-4.0.0.tgz</b></p></summary>
<p>Sinatra inspired web development framework</p>
... | non_defect | express tgz vulnerabilities highest severity is autoclosed vulnerable library express tgz sinatra inspired web development framework library home page a href path to dependency file package json path to vulnerable library node modules express package json found ... | 0 |
126,083 | 4,972,042,128 | IssuesEvent | 2016-12-05 20:24:23 | TheScienceMuseum/collectionsonline | https://api.github.com/repos/TheScienceMuseum/collectionsonline | opened | Styling of single taxonomy term | enhancement Post-Beta-Launch priority-3 | Not sure if something just hasn't loaded for me / but if we only have a sign term it should probably left align.
<img width="522" alt="screen shot 2016-12-05 at 20 23 17" src="https://cloud.githubusercontent.com/assets/91365/20901055/b420c1ac-bb28-11e6-8427-0be5babc3622.png"> | 1.0 | Styling of single taxonomy term - Not sure if something just hasn't loaded for me / but if we only have a sign term it should probably left align.
<img width="522" alt="screen shot 2016-12-05 at 20 23 17" src="https://cloud.githubusercontent.com/assets/91365/20901055/b420c1ac-bb28-11e6-8427-0be5babc3622.png"> | non_defect | styling of single taxonomy term not sure if something just hasn t loaded for me but if we only have a sign term it should probably left align img width alt screen shot at src | 0 |
229,261 | 7,573,325,125 | IssuesEvent | 2018-04-23 17:25:52 | datahq/datahub-qa | https://api.github.com/repos/datahq/datahub-qa | closed | Possible resource path related issue in Windows | Priority ★★ Severity: Major | Looking at this report, I'm not sure if it's happening because user provided the wrong path to a resource or our code behaves differently in the Windows OS:
https://sentry.io/share/issue/18b80085753f44ecae1bbfb641d0d11a/
as you can see a path to a resource was considered as relative to dp.json.
## Tasks
* [... | 1.0 | Possible resource path related issue in Windows - Looking at this report, I'm not sure if it's happening because user provided the wrong path to a resource or our code behaves differently in the Windows OS:
https://sentry.io/share/issue/18b80085753f44ecae1bbfb641d0d11a/
as you can see a path to a resource was con... | non_defect | possible resource path related issue in windows looking at this report i m not sure if it s happening because user provided the wrong path to a resource or our code behaves differently in the windows os as you can see a path to a resource was considered as relative to dp json tasks try to repr... | 0 |
8,990 | 2,615,117,423 | IssuesEvent | 2015-03-01 05:42:47 | chrsmith/google-api-java-client | https://api.github.com/repos/chrsmith/google-api-java-client | closed | UnsupportedOperationException when using AndroidXmlParserFactory | auto-migrated Component-XML Milestone-Version1.4.0 Priority-High Type-Defect | ```
Version of google-api-java-client (e.g. 1.2.1-alpha)?
1.2.1-alpha
Java environment (e.g. Java 6, Android 2.2, App Engine 1.3.7)?
Android 2.2 emulator
Describe the problem.
Set the parser factory to use Android's native XML pull parser using:
Xml.parserFactory = new AndroidXmlParserFactory();
And when tryin... | 1.0 | UnsupportedOperationException when using AndroidXmlParserFactory - ```
Version of google-api-java-client (e.g. 1.2.1-alpha)?
1.2.1-alpha
Java environment (e.g. Java 6, Android 2.2, App Engine 1.3.7)?
Android 2.2 emulator
Describe the problem.
Set the parser factory to use Android's native XML pull parser using:
... | defect | unsupportedoperationexception when using androidxmlparserfactory version of google api java client e g alpha alpha java environment e g java android app engine android emulator describe the problem set the parser factory to use android s native xml pull parser using ... | 1 |
8,801 | 2,612,896,978 | IssuesEvent | 2015-02-27 17:22:43 | chrsmith/windows-package-manager | https://api.github.com/repos/chrsmith/windows-package-manager | closed | Does windows-package-manager handle updates? | auto-migrated Milestone-1.13.0 Type-Defect | ```
(Great application - just found it today and love it already.)
My 'bug' is a usability issue.
Users used to package managers in Linux systems will assume that WPM handles
updates, but I can't find any mention of that issue. I think it needs to be
noted somewhere if WPM does not deal with upgrades, or if this is... | 1.0 | Does windows-package-manager handle updates? - ```
(Great application - just found it today and love it already.)
My 'bug' is a usability issue.
Users used to package managers in Linux systems will assume that WPM handles
updates, but I can't find any mention of that issue. I think it needs to be
noted somewhere if... | defect | does windows package manager handle updates great application just found it today and love it already my bug is a usability issue users used to package managers in linux systems will assume that wpm handles updates but i can t find any mention of that issue i think it needs to be noted somewhere if... | 1 |
70,599 | 23,259,126,482 | IssuesEvent | 2022-08-04 12:02:37 | primefaces/primeng | https://api.github.com/repos/primefaces/primeng | opened | p-multiselect: Performance fix when selecting all items (10000 records or more) the dropdown hangs | defect | ### Describe the bug
When you have large data set in a dropdown, let's say 10K records, the dropdown hangs for a while and when it shows up and you click selectAll, you have to wait forever.
### Environment
Angular v13
### Reproducer
_No response_
### Angular version
13
### PrimeNG version
13.3.3
### Build / ... | 1.0 | p-multiselect: Performance fix when selecting all items (10000 records or more) the dropdown hangs - ### Describe the bug
When you have large data set in a dropdown, let's say 10K records, the dropdown hangs for a while and when it shows up and you click selectAll, you have to wait forever.
### Environment
Angular v... | defect | p multiselect performance fix when selecting all items records or more the dropdown hangs describe the bug when you have large data set in a dropdown let s say records the dropdown hangs for a while and when it shows up and you click selectall you have to wait forever environment angular ... | 1 |
70,955 | 23,389,583,211 | IssuesEvent | 2022-08-11 16:29:12 | EnvironmentOntology/envo | https://api.github.com/repos/EnvironmentOntology/envo | closed | Create a termgenie for ENVO | auto-migrated Type-Defect | ```
Similar to
go.termgenie.org
oba.termgenie.org
```
Original issue reported on code.google.com by `cmung...@gmail.com` on 22 Dec 2013 at 6:57
| 1.0 | Create a termgenie for ENVO - ```
Similar to
go.termgenie.org
oba.termgenie.org
```
Original issue reported on code.google.com by `cmung...@gmail.com` on 22 Dec 2013 at 6:57
| defect | create a termgenie for envo similar to go termgenie org oba termgenie org original issue reported on code google com by cmung gmail com on dec at | 1 |
27,908 | 5,120,243,410 | IssuesEvent | 2017-01-09 01:45:33 | jccastillo0007/eFacturaT | https://api.github.com/repos/jccastillo0007/eFacturaT | closed | Complemento Nomina 1.2 - No acepta la entidad federativa querétaro | bug defect | No sé si está mal nuestro catálogo o el del PAC, pero no acepta Querétaro... y aquí tenemos varias nómina...:( | 1.0 | Complemento Nomina 1.2 - No acepta la entidad federativa querétaro - No sé si está mal nuestro catálogo o el del PAC, pero no acepta Querétaro... y aquí tenemos varias nómina...:( | defect | complemento nomina no acepta la entidad federativa querétaro no sé si está mal nuestro catálogo o el del pac pero no acepta querétaro y aquí tenemos varias nómina | 1 |
3,845 | 2,610,070,037 | IssuesEvent | 2015-02-26 18:20:32 | chrsmith/jsjsj122 | https://api.github.com/repos/chrsmith/jsjsj122 | opened | 台州割包茎去哪家医院最好 | auto-migrated Priority-Medium Type-Defect | ```
台州割包茎去哪家医院最好【台州五洲生殖医院】24小时健康
咨询热线:0576-88066933-(扣扣800080609)-(微信号tzwzszyy)医院地址:台
州市椒江区枫南路229号(枫南大转盘旁)乘车线路:乘坐104、1
08、118、198及椒江一金清公交车直达枫南小区,乘坐107、105、
109、112、901、 902公交车到星星广场下车,步行即可到院。
诊疗项目:阳痿,早泄,前列腺炎,前列腺增生,龟头炎,��
�精,无精。包皮包茎,精索静脉曲张,淋病等。
台州五洲生殖医院是台州最大的男科医院,权威专家在线免��
�咨询,拥有专业完善的男科检查治疗设备,严格按照国家标�
��收费。尖端医疗设备,与世界同步。权... | 1.0 | 台州割包茎去哪家医院最好 - ```
台州割包茎去哪家医院最好【台州五洲生殖医院】24小时健康
咨询热线:0576-88066933-(扣扣800080609)-(微信号tzwzszyy)医院地址:台
州市椒江区枫南路229号(枫南大转盘旁)乘车线路:乘坐104、1
08、118、198及椒江一金清公交车直达枫南小区,乘坐107、105、
109、112、901、 902公交车到星星广场下车,步行即可到院。
诊疗项目:阳痿,早泄,前列腺炎,前列腺增生,龟头炎,��
�精,无精。包皮包茎,精索静脉曲张,淋病等。
台州五洲生殖医院是台州最大的男科医院,权威专家在线免��
�咨询,拥有专业完善的男科检查治疗设备,严格按照国家标�
��收费... | defect | 台州割包茎去哪家医院最好 台州割包茎去哪家医院最好【台州五洲生殖医院】 咨询热线 微信号tzwzszyy 医院地址 台 (枫南大转盘旁)乘车线路 、 、 、 , 、 、 、 、 、 ,步行即可到院。 诊疗项目:阳痿,早泄,前列腺炎,前列腺增生,龟头炎,�� �精,无精。包皮包茎,精索静脉曲张,淋病等。 台州五洲生殖医院是台州最大的男科医院,权威专家在线免�� �咨询,拥有专业完善的男科检查治疗设备,严格按照国家标� ��收费。尖端医疗设备,与世界同步。权威专家,成就专业典 范。人性化服务,一切以患者为中心。 看男科就选台州五洲生殖医院,专业男科为男人。 origina... | 1 |
60,121 | 12,058,795,124 | IssuesEvent | 2020-04-15 18:05:49 | home-assistant/brands | https://api.github.com/repos/home-assistant/brands | closed | Kodi is missing brand images | domain-missing has-codeowner |
## The problem
The Kodi integration does not have brand images in
this repository.
We recently started this Brands repository, to create a centralized storage of all brand-related images. These images are used on our website and the Home Assistant frontend.
The following images are missing and would ideally be ... | 1.0 | Kodi is missing brand images -
## The problem
The Kodi integration does not have brand images in
this repository.
We recently started this Brands repository, to create a centralized storage of all brand-related images. These images are used on our website and the Home Assistant frontend.
The following images ar... | non_defect | kodi is missing brand images the problem the kodi integration does not have brand images in this repository we recently started this brands repository to create a centralized storage of all brand related images these images are used on our website and the home assistant frontend the following images ar... | 0 |
61,158 | 17,023,620,454 | IssuesEvent | 2021-07-03 02:57:52 | tomhughes/trac-tickets | https://api.github.com/repos/tomhughes/trac-tickets | closed | Potlatch drops a tag on edit of a similar one using suggested popups | Component: potlatch (flash editor) Priority: critical Resolution: wontfix Type: defect | **[Submitted to the original trac issue database at 5.25pm, Sunday, 1st August 2010]**
Potlatch quietly looses a tag (ex:"name") when one adds another tag with a similar name (ex:"name:hu"), if one TYPES the exact name of the first tag (type:'name') then SELECTS with the mouse the suggested popup (select:'name:hu') wh... | 1.0 | Potlatch drops a tag on edit of a similar one using suggested popups - **[Submitted to the original trac issue database at 5.25pm, Sunday, 1st August 2010]**
Potlatch quietly looses a tag (ex:"name") when one adds another tag with a similar name (ex:"name:hu"), if one TYPES the exact name of the first tag (type:'name'... | defect | potlatch drops a tag on edit of a similar one using suggested popups potlatch quietly looses a tag ex name when one adds another tag with a similar name ex name hu if one types the exact name of the first tag type name then selects with the mouse the suggested popup select name hu which appear... | 1 |
21,078 | 3,456,625,435 | IssuesEvent | 2015-12-18 02:51:16 | dart-lang/sdk | https://api.github.com/repos/dart-lang/sdk | opened | cps_ir: statement names are unstable and not minified | area-dart2js dart2js-nssa Type-Defect | Statement labels should restart with each new function. L25 is because L1..L24 is used in other functions. This causes names to be longer than necessary, and widespread gratuitous differences when a single function or compilation order changes.
```js
findFeed$1: function(id_) {
var v0 = J.ArrayItera... | 1.0 | cps_ir: statement names are unstable and not minified - Statement labels should restart with each new function. L25 is because L1..L24 is used in other functions. This causes names to be longer than necessary, and widespread gratuitous differences when a single function or compilation order changes.
```js
f... | defect | cps ir statement names are unstable and not minified statement labels should restart with each new function is because is used in other functions this causes names to be longer than necessary and widespread gratuitous differences when a single function or compilation order changes js findfe... | 1 |
47,605 | 13,065,855,109 | IssuesEvent | 2020-07-30 20:32:58 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | closed | [COGNITION, SCREENREADER]: Dates SHOULD be spelled out, as documented in the VA design system | 508-defect-1 508-issue-cognition 508/Accessibility blocked frontend vsa vsa-ebenefits | # [508-defect-1 :exclamation: Launchblocker](https://github.com/department-of-veterans-affairs/va.gov-team/blob/master/platform/accessibility/guidance/defect-severity-rubric.md#508-defect-1)
**Feedback framework**
- **❗️ Must** for if the feedback must be applied
- **⚠️Should** if the feedback is best practice... | 1.0 | [COGNITION, SCREENREADER]: Dates SHOULD be spelled out, as documented in the VA design system - # [508-defect-1 :exclamation: Launchblocker](https://github.com/department-of-veterans-affairs/va.gov-team/blob/master/platform/accessibility/guidance/defect-severity-rubric.md#508-defect-1)
**Feedback framework**
- *... | defect | dates should be spelled out as documented in the va design system feedback framework ❗️ must for if the feedback must be applied ⚠️should if the feedback is best practice ✔️ consider for suggestions enhancements description the specifies dates should spell ... | 1 |
58,976 | 16,985,598,099 | IssuesEvent | 2021-06-30 14:04:26 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | opened | should getDistributedObjects include `__sql.catalog` map ? | Module: SQL Team: Core Type: Defect | **Describe the bug**
I think this is an internal map for SQL and should be hidden.
**Expected behavior**
I expect it to be filtered from getDistributedObjects results.
**To Reproduce**
Steps to reproduce the behavior:
1. Run 5.0 snapshot server(latest) `docker run -p 5701:5701 hazelcast/hazelcast:5.0-SNAPSH... | 1.0 | should getDistributedObjects include `__sql.catalog` map ? - **Describe the bug**
I think this is an internal map for SQL and should be hidden.
**Expected behavior**
I expect it to be filtered from getDistributedObjects results.
**To Reproduce**
Steps to reproduce the behavior:
1. Run 5.0 snapshot server(la... | defect | should getdistributedobjects include sql catalog map describe the bug i think this is an internal map for sql and should be hidden expected behavior i expect it to be filtered from getdistributedobjects results to reproduce steps to reproduce the behavior run snapshot server la... | 1 |
70,799 | 15,110,265,625 | IssuesEvent | 2021-02-08 18:58:53 | gwen-bo/BAP-online | https://api.github.com/repos/gwen-bo/BAP-online | closed | Firestore rules | afwerking security | Firestore rules aanpassen/ beter beveiligen vóór productie (!)
- regels per collection
1. interactie: (update:true/write:if)
2. users: (read: true/ write: if)
3. auteurs (read: true/ write: false)
4. allow-users (read/write: false)
- functie check if data.name is bestaande in allow-users collection:
functio... | True | Firestore rules - Firestore rules aanpassen/ beter beveiligen vóór productie (!)
- regels per collection
1. interactie: (update:true/write:if)
2. users: (read: true/ write: if)
3. auteurs (read: true/ write: false)
4. allow-users (read/write: false)
- functie check if data.name is bestaande in allow-users col... | non_defect | firestore rules firestore rules aanpassen beter beveiligen vóór productie regels per collection interactie update true write if users read true write if auteurs read true write false allow users read write false functie check if data name is bestaande in allow users col... | 0 |
67,622 | 21,033,444,500 | IssuesEvent | 2022-03-31 04:39:18 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | Changing theme from Dark to Light does not take effect. | T-Defect | ### Steps to reproduce
https://user-images.githubusercontent.com/63562663/160946884-0d80a580-650f-4f29-8fa7-96a87d77cbaf.mp4
### Outcome
#### What did you expect?
Change theme to Light mode
#### What happened instead?
Dark mode persisted after changing to Light mode
### Operating system
Windows... | 1.0 | Changing theme from Dark to Light does not take effect. - ### Steps to reproduce
https://user-images.githubusercontent.com/63562663/160946884-0d80a580-650f-4f29-8fa7-96a87d77cbaf.mp4
### Outcome
#### What did you expect?
Change theme to Light mode
#### What happened instead?
Dark mode persisted after ... | defect | changing theme from dark to light does not take effect steps to reproduce outcome what did you expect change theme to light mode what happened instead dark mode persisted after changing to light mode operating system windows application version version ... | 1 |
321,085 | 23,838,844,797 | IssuesEvent | 2022-09-06 08:35:20 | alphagov/govuk-prototype-kit | https://api.github.com/repos/alphagov/govuk-prototype-kit | closed | Update accessibility statement | documentation accessibility 🕔 hours | ## What
With the fix for step by step completed in release v13.0.0, the documentation site is now accessible with all outstanding issues from the accessibility audit addressed and fixed.
## Related documentation
GOV.UK Prototype Kit accessibility statement: https://govuk-prototype-kit.herokuapp.com/docs/accessibil... | 1.0 | Update accessibility statement - ## What
With the fix for step by step completed in release v13.0.0, the documentation site is now accessible with all outstanding issues from the accessibility audit addressed and fixed.
## Related documentation
GOV.UK Prototype Kit accessibility statement: https://govuk-prototype-... | non_defect | update accessibility statement what with the fix for step by step completed in release the documentation site is now accessible with all outstanding issues from the accessibility audit addressed and fixed related documentation gov uk prototype kit accessibility statement who content desig... | 0 |
55,407 | 30,737,439,504 | IssuesEvent | 2023-07-28 08:47:24 | flutter/flutter | https://api.github.com/repos/flutter/flutter | opened | FlutterViewController doesn't call deinit when page is closed and result in memory leak problem | from: performance template | <!-- Thank you for using Flutter!
If you are looking for support, please check out our documentation
or consider asking a question on Stack Overflow:
* https://flutter.dev/
* https://api.flutter.dev/
* https://stackoverflow.com/questions/tagged/flutter?sort=frequent
If you hav... | True | FlutterViewController doesn't call deinit when page is closed and result in memory leak problem - <!-- Thank you for using Flutter!
If you are looking for support, please check out our documentation
or consider asking a question on Stack Overflow:
* https://flutter.dev/
* https://api.flutter... | non_defect | flutterviewcontroller doesn t call deinit when page is closed and result in memory leak problem thank you for using flutter if you are looking for support please check out our documentation or consider asking a question on stack overflow if you have found... | 0 |
60,300 | 25,080,424,721 | IssuesEvent | 2022-11-07 18:48:49 | hashicorp/terraform-provider-aws | https://api.github.com/repos/hashicorp/terraform-provider-aws | closed | [Bug]: The aws_secretmanager_secret_rotation plan file includes a `tags` field but tags aren't supported | bug service/secretsmanager | ### Terraform Core Version
1.3.4
### AWS Provider Version
4.38.0
### Affected Resource(s)
The `aws_secretsmanager_secret_rotation` resource produces a plan that contains a `tags` field even though the [Rotate Secret API](https://docs.aws.amazon.com/secretsmanager/latest/apireference/API_RotateSecret.html... | 1.0 | [Bug]: The aws_secretmanager_secret_rotation plan file includes a `tags` field but tags aren't supported - ### Terraform Core Version
1.3.4
### AWS Provider Version
4.38.0
### Affected Resource(s)
The `aws_secretsmanager_secret_rotation` resource produces a plan that contains a `tags` field even though t... | non_defect | the aws secretmanager secret rotation plan file includes a tags field but tags aren t supported terraform core version aws provider version affected resource s the aws secretsmanager secret rotation resource produces a plan that contains a tags field even though the ... | 0 |
24,024 | 3,900,020,094 | IssuesEvent | 2016-04-18 02:06:05 | networkx/networkx | https://api.github.com/repos/networkx/networkx | closed | Namespace collision on nx.generators | Defect | It looks like nx.generators is no longer the modules in the folder networkx/generators. Instead it is the contents of networkx/algorithms/community/generators.py
Can we rename that file to avoid namespace collisions on the word generators?
Maybe it should be moved to the generators directory and called ```communit... | 1.0 | Namespace collision on nx.generators - It looks like nx.generators is no longer the modules in the folder networkx/generators. Instead it is the contents of networkx/algorithms/community/generators.py
Can we rename that file to avoid namespace collisions on the word generators?
Maybe it should be moved to the gene... | defect | namespace collision on nx generators it looks like nx generators is no longer the modules in the folder networkx generators instead it is the contents of networkx algorithms community generators py can we rename that file to avoid namespace collisions on the word generators maybe it should be moved to the gene... | 1 |
46,508 | 13,055,923,985 | IssuesEvent | 2020-07-30 03:08:05 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | opened | cmake/tools - cmake can't find cdk in cvmfs (Trac #1334) | Incomplete Migration Migrated from Trac cmake defect | Migrated from https://code.icecube.wisc.edu/ticket/1334
```json
{
"status": "closed",
"changetime": "2016-03-18T21:14:15",
"description": "morax is picking up cdk in /usr/local, not from cvmfs",
"reporter": "nega",
"cc": "david.schultz",
"resolution": "worksforme",
"_ts": "145833565584... | 1.0 | cmake/tools - cmake can't find cdk in cvmfs (Trac #1334) - Migrated from https://code.icecube.wisc.edu/ticket/1334
```json
{
"status": "closed",
"changetime": "2016-03-18T21:14:15",
"description": "morax is picking up cdk in /usr/local, not from cvmfs",
"reporter": "nega",
"cc": "david.schultz",... | defect | cmake tools cmake can t find cdk in cvmfs trac migrated from json status closed changetime description morax is picking up cdk in usr local not from cvmfs reporter nega cc david schultz resolution worksforme ts ... | 1 |
61,368 | 17,023,677,673 | IssuesEvent | 2021-07-03 03:15:14 | tomhughes/trac-tickets | https://api.github.com/repos/tomhughes/trac-tickets | closed | osm2pgsql does not build on Arch Linux | Component: osm2pgsql Priority: major Resolution: worksforme Type: defect | **[Submitted to the original trac issue database at 10.34pm, Wednesday, 2nd February 2011]**
Running yaourt -S osm2pgsql-svn fails with:
```
Checked out revision 25215.
SVN checkout done or server timeout
==> Starting make...
sed: can't read Makefile.in: No such file or directory
Aborting...
==> ERROR: Makepkg ... | 1.0 | osm2pgsql does not build on Arch Linux - **[Submitted to the original trac issue database at 10.34pm, Wednesday, 2nd February 2011]**
Running yaourt -S osm2pgsql-svn fails with:
```
Checked out revision 25215.
SVN checkout done or server timeout
==> Starting make...
sed: can't read Makefile.in: No such file or di... | defect | does not build on arch linux running yaourt s svn fails with checked out revision svn checkout done or server timeout starting make sed can t read makefile in no such file or directory aborting error makepkg was unable to build svn tried to modify the pkgbuild to m... | 1 |
63,263 | 15,529,840,684 | IssuesEvent | 2021-03-13 16:45:24 | opencv/opencv | https://api.github.com/repos/opencv/opencv | closed | PPC64: Unable to detect CPU features when optimization is disabled | affected: 3.4 bug category: build/install category: core platform: ppc (PowerPC) | which leads to a fatal error during initializing the core module if build option `DCV_ENABLE_INTRINSICS` was off.
#### Error message:
```Bash
******************************************************************
* FATAL ERROR: *
* This OpenCV build doesn't support c... | 1.0 | PPC64: Unable to detect CPU features when optimization is disabled - which leads to a fatal error during initializing the core module if build option `DCV_ENABLE_INTRINSICS` was off.
#### Error message:
```Bash
******************************************************************
* FATAL ERROR: ... | non_defect | unable to detect cpu features when optimization is disabled which leads to a fatal error during initializing the core module if build option dcv enable intrinsics was off error message bash fatal error ... | 0 |
96,150 | 3,965,256,048 | IssuesEvent | 2016-05-03 07:19:56 | Titanburg/band-uniform | https://api.github.com/repos/Titanburg/band-uniform | closed | DEV-5 Research Android Studio | Non-Functional Priority - M Story | As a developer, I want to understand how to use Android Studio, so I can build an app.
Priority: M
Estimate: 8h
Acceptance Criterion:
1. Read information about Android Studio
2. Install Android Studio
3. Create first app. | 1.0 | DEV-5 Research Android Studio - As a developer, I want to understand how to use Android Studio, so I can build an app.
Priority: M
Estimate: 8h
Acceptance Criterion:
1. Read information about Android Studio
2. Install Android Studio
3. Create first app. | non_defect | dev research android studio as a developer i want to understand how to use android studio so i can build an app priority m estimate acceptance criterion read information about android studio install android studio create first app | 0 |
218,750 | 17,019,579,971 | IssuesEvent | 2021-07-02 16:41:48 | near/nearcore | https://api.github.com/repos/near/nearcore | closed | Fix all nightly tests | A-testing C-epic S-stale | This issue tracks our progress in fixing all nightly tests. For those tests that are flaky in nature, we should either disable it or find a way to remove the flakiness. | 1.0 | Fix all nightly tests - This issue tracks our progress in fixing all nightly tests. For those tests that are flaky in nature, we should either disable it or find a way to remove the flakiness. | non_defect | fix all nightly tests this issue tracks our progress in fixing all nightly tests for those tests that are flaky in nature we should either disable it or find a way to remove the flakiness | 0 |
58,763 | 16,747,818,748 | IssuesEvent | 2021-06-11 17:58:25 | idaholab/moose | https://api.github.com/repos/idaholab/moose | opened | ContactSplit setup PETSc error | P: normal T: defect | ## Bug Description
<!--A clear and concise description of the problem (Note: A missing feature is not a bug).-->
There is a PETSc error when using ContactSplit preconditioner for certain applications. Refs #17501
It seems all PETSc options are not correcly flow into PETSc, and PETSc an not setup a preconditioner.... | 1.0 | ContactSplit setup PETSc error - ## Bug Description
<!--A clear and concise description of the problem (Note: A missing feature is not a bug).-->
There is a PETSc error when using ContactSplit preconditioner for certain applications. Refs #17501
It seems all PETSc options are not correcly flow into PETSc, and PET... | defect | contactsplit setup petsc error bug description there is a petsc error when using contactsplit preconditioner for certain applications refs it seems all petsc options are not correcly flow into petsc and petsc an not setup a preconditioner it is likely because we are recreating nonlinear solvers ma... | 1 |
174,569 | 13,495,578,428 | IssuesEvent | 2020-09-12 00:18:51 | rancher/rke2 | https://api.github.com/repos/rancher/rke2 | closed | Update To Only Apply Network Policy if in CIS Mode | [zube]: To Test | Currently, the code applies a network policy regardless of whether the user has specified CIS mode or not. This needs to be changed to only apply the policy if in CIS mode.
The policy should also allow for DNS to be passed to kube-system namespace. | 1.0 | Update To Only Apply Network Policy if in CIS Mode - Currently, the code applies a network policy regardless of whether the user has specified CIS mode or not. This needs to be changed to only apply the policy if in CIS mode.
The policy should also allow for DNS to be passed to kube-system namespace. | non_defect | update to only apply network policy if in cis mode currently the code applies a network policy regardless of whether the user has specified cis mode or not this needs to be changed to only apply the policy if in cis mode the policy should also allow for dns to be passed to kube system namespace | 0 |
58,020 | 7,112,817,485 | IssuesEvent | 2018-01-17 18:17:08 | phetsims/masses-and-springs | https://api.github.com/repos/phetsims/masses-and-springs | closed | Reducing floating boxes | design:polish meeting:design | @arouinfar here are some suggestions from @emily-phet - might be worth discussing at a future design meeting. I think there are a few places we could reduce the feeling of many floating control boxes (eg the spring constant controls may not even need a box, also possible the check boxes do not need a box).
@emily-p... | 2.0 | Reducing floating boxes - @arouinfar here are some suggestions from @emily-phet - might be worth discussing at a future design meeting. I think there are a few places we could reduce the feeling of many floating control boxes (eg the spring constant controls may not even need a box, also possible the check boxes do not... | non_defect | reducing floating boxes arouinfar here are some suggestions from emily phet might be worth discussing at a future design meeting i think there are a few places we could reduce the feeling of many floating control boxes eg the spring constant controls may not even need a box also possible the check boxes do not... | 0 |
16,295 | 2,889,333,149 | IssuesEvent | 2015-06-13 09:54:56 | kuribot/boilerpipe | https://api.github.com/repos/kuribot/boilerpipe | closed | Server returned HTTP response code: 403 for URL (SOLVED) please use this codeline. | auto-migrated Priority-Medium Type-Defect | ```
Instead of using URLConnection in java, if you use HttpURLConnection
we can able to access the requested web page from java.
Try the following code
HttpURLConnection httpcon = (HttpURLConnection) url.openConnection();
httpcon.addRequestProperty("User-Agent", "Mozilla/4.76");
Normal java using urlConnection wont... | 1.0 | Server returned HTTP response code: 403 for URL (SOLVED) please use this codeline. - ```
Instead of using URLConnection in java, if you use HttpURLConnection
we can able to access the requested web page from java.
Try the following code
HttpURLConnection httpcon = (HttpURLConnection) url.openConnection();
httpcon.add... | defect | server returned http response code for url solved please use this codeline instead of using urlconnection in java if you use httpurlconnection we can able to access the requested web page from java try the following code httpurlconnection httpcon httpurlconnection url openconnection httpcon addre... | 1 |
228,955 | 18,273,022,926 | IssuesEvent | 2021-10-04 15:35:49 | kubernetes-sigs/cluster-api-provider-azure | https://api.github.com/repos/kubernetes-sigs/cluster-api-provider-azure | closed | GPU test is flaky | kind/failing-test | /kind bug
[Before submitting an issue, have you checked the [Troubleshooting Guide](https://capz.sigs.k8s.io/topics/troubleshooting.html)?]
**What steps did you take and what happened:**
[A clear and concise description of what the bug is.]
https://testgrid.k8s.io/sig-cluster-lifecycle-cluster-api-provider-az... | 1.0 | GPU test is flaky - /kind bug
[Before submitting an issue, have you checked the [Troubleshooting Guide](https://capz.sigs.k8s.io/topics/troubleshooting.html)?]
**What steps did you take and what happened:**
[A clear and concise description of what the bug is.]
https://testgrid.k8s.io/sig-cluster-lifecycle-clu... | non_defect | gpu test is flaky kind bug what steps did you take and what happened is failing at around rate the first step in investigating this would be to look at failures and add more details to this issue about what error s is are happening anything else you would like to add e... | 0 |
51,503 | 7,707,792,279 | IssuesEvent | 2018-05-22 00:52:18 | chrissimpkins/Crunch | https://api.github.com/repos/chrissimpkins/Crunch | opened | Autoupdate macOS GUI with Homebrew cask | documentation | Homebrew cask now supports the following command which will automatically update the Crunch macOS GUI installed through Homebrew cask to new releases since you last installed/updated:
```
$ homebrew cask upgrade
```
Thanks to @adidalal for this information in https://github.com/chrissimpkins/Crunch/issues/49#is... | 1.0 | Autoupdate macOS GUI with Homebrew cask - Homebrew cask now supports the following command which will automatically update the Crunch macOS GUI installed through Homebrew cask to new releases since you last installed/updated:
```
$ homebrew cask upgrade
```
Thanks to @adidalal for this information in https://gi... | non_defect | autoupdate macos gui with homebrew cask homebrew cask now supports the following command which will automatically update the crunch macos gui installed through homebrew cask to new releases since you last installed updated homebrew cask upgrade thanks to adidalal for this information in will up... | 0 |
46,917 | 13,056,002,131 | IssuesEvent | 2020-07-30 03:21:29 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | opened | Inconsistent segment parameter requirements (Trac #2135) | Incomplete Migration Migrated from Trac combo core defect | Migrated from https://code.icecube.wisc.edu/ticket/2135
```json
{
"status": "closed",
"changetime": "2019-01-11T21:03:41",
"description": "`I3Tray.AddSegment` assumes that segments take two parameters (the tray and a name), but `icetray.traysegment` enforces only that they must have one parameter (the tra... | 1.0 | Inconsistent segment parameter requirements (Trac #2135) - Migrated from https://code.icecube.wisc.edu/ticket/2135
```json
{
"status": "closed",
"changetime": "2019-01-11T21:03:41",
"description": "`I3Tray.AddSegment` assumes that segments take two parameters (the tray and a name), but `icetray.traysegmen... | defect | inconsistent segment parameter requirements trac migrated from json status closed changetime description addsegment assumes that segments take two parameters the tray and a name but icetray traysegment enforces only that they must have one parameter the tr... | 1 |
39,923 | 9,745,409,420 | IssuesEvent | 2019-06-03 09:33:27 | jOOQ/jOOQ | https://api.github.com/repos/jOOQ/jOOQ | closed | Translator loses quoted names | C: Parser E: All Editions P: Medium R: Fixed T: Defect | The current version of the translator is losing quoted names:
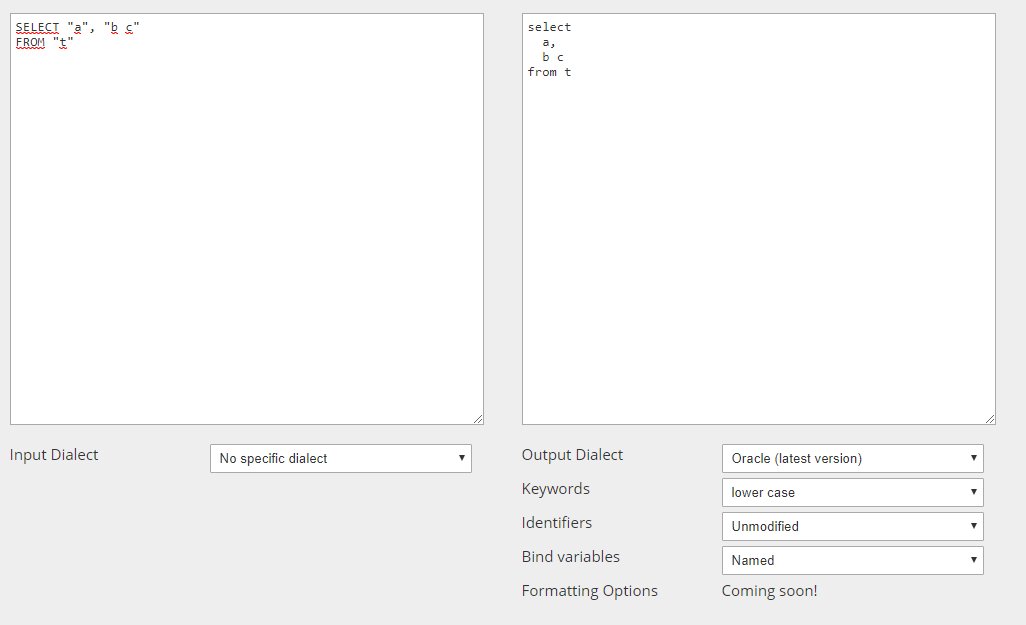
This is because https://github.com/jOOQ/jOOQ/issues/5909 has not yet been applied to the translator. | 1.0 | Translator loses quoted names - The current version of the translator is losing quoted names:
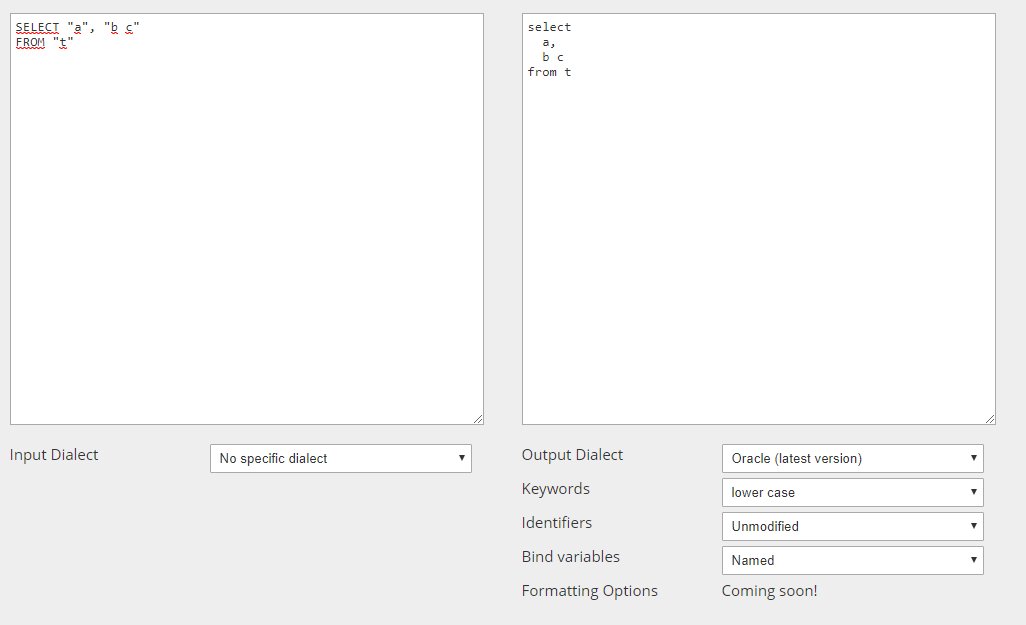
This is because https://github.com/jOOQ/jOOQ/issues/5909 has not yet been applied to the translator. | defect | translator loses quoted names the current version of the translator is losing quoted names this is because has not yet been applied to the translator | 1 |
80,295 | 30,216,726,040 | IssuesEvent | 2023-07-05 16:04:46 | SeleniumHQ/selenium | https://api.github.com/repos/SeleniumHQ/selenium | opened | [🐛 Bug]: `Selenium.Support.StrongNamed` depends on `Selenium.WebDeriver` instead of strong name signed version | I-defect needs-triaging | ### What happened?
`Selenium.Support.StrongNamed` package (available [here](https://github.com/SeleniumHQ/selenium/releases/download/selenium-4.8.0/selenium-dotnet-strongnamed-4.8.2.zip))depends on `Selenium.WebDeriver` instead of strong name signed version: `Selenium.WebDeriver.StrongNamed`.
Also this may cause bu... | 1.0 | [🐛 Bug]: `Selenium.Support.StrongNamed` depends on `Selenium.WebDeriver` instead of strong name signed version - ### What happened?
`Selenium.Support.StrongNamed` package (available [here](https://github.com/SeleniumHQ/selenium/releases/download/selenium-4.8.0/selenium-dotnet-strongnamed-4.8.2.zip))depends on `Seleni... | defect | selenium support strongnamed depends on selenium webderiver instead of strong name signed version what happened selenium support strongnamed package available on selenium webderiver instead of strong name signed version selenium webderiver strongnamed also this may cause build issues when... | 1 |
481,976 | 13,895,037,113 | IssuesEvent | 2020-10-19 15:22:31 | trezor/trezor-suite | https://api.github.com/repos/trezor/trezor-suite | closed | Empty screen after update succeeds. | Bug High priority | **Info:**
- OS: macOS 10.14.6
- Suite Version: macOS, 20.10.1
- Firmware Version: Model T, update to 2.3.4
**Describe the bug**
Empty screen in Suite after the firmware update finishes. Clears after the device is unlocked. Not a serious issue, it just looks like Suite is stuck (see screenshot).
**Steps t... | 1.0 | Empty screen after update succeeds. - **Info:**
- OS: macOS 10.14.6
- Suite Version: macOS, 20.10.1
- Firmware Version: Model T, update to 2.3.4
**Describe the bug**
Empty screen in Suite after the firmware update finishes. Clears after the device is unlocked. Not a serious issue, it just looks like Suite i... | non_defect | empty screen after update succeeds info os macos suite version macos firmware version model t update to describe the bug empty screen in suite after the firmware update finishes clears after the device is unlocked not a serious issue it just looks like suite is st... | 0 |
62,354 | 25,966,761,380 | IssuesEvent | 2022-12-19 07:48:29 | Azure/azure-powershell | https://api.github.com/repos/Azure/azure-powershell | closed | Az.Synapse - Set linkedService cmd not working | Service Attention question Synapse | <!--
- Make sure you are able to reproduce this issue on the latest released version of Az
- https://www.powershellgallery.com/packages/Az
- Please search the existing issues to see if there has been a similar issue filed
- For issue related to importing a module, please refer to our troubleshooting guide:
... | 1.0 | Az.Synapse - Set linkedService cmd not working - <!--
- Make sure you are able to reproduce this issue on the latest released version of Az
- https://www.powershellgallery.com/packages/Az
- Please search the existing issues to see if there has been a similar issue filed
- For issue related to importing a modu... | non_defect | az synapse set linkedservice cmd not working make sure you are able to reproduce this issue on the latest released version of az please search the existing issues to see if there has been a similar issue filed for issue related to importing a module please refer to our troubleshooting guid... | 0 |
32,101 | 6,715,067,041 | IssuesEvent | 2017-10-13 19:30:06 | scipy/scipy | https://api.github.com/repos/scipy/scipy | closed | scipy 1.0.0rc1 windows wheels depend on missing msvcp140.dll | defect Official binaries | Importing `scipy.sparse` or `scipy.special` (from 1.0.0rc1 openblas linked wheels) on windows can fail with an ImportError if the target machine does not have msvcp140.dll (part of MS Visual C++ 2015 redistributable package) installed.
### Reproducing code example:
```
pip install scipy==1.0.0rc1
python -c"import... | 1.0 | scipy 1.0.0rc1 windows wheels depend on missing msvcp140.dll - Importing `scipy.sparse` or `scipy.special` (from 1.0.0rc1 openblas linked wheels) on windows can fail with an ImportError if the target machine does not have msvcp140.dll (part of MS Visual C++ 2015 redistributable package) installed.
### Reproducing co... | defect | scipy windows wheels depend on missing dll importing scipy sparse or scipy special from openblas linked wheels on windows can fail with an importerror if the target machine does not have dll part of ms visual c redistributable package installed reproducing code example pip i... | 1 |
81,856 | 31,773,565,799 | IssuesEvent | 2023-09-12 13:13:42 | vector-im/element-x-android | https://api.github.com/repos/vector-im/element-x-android | closed | Reply action: harmonize condition | S-Minor T-Defect O-Uncommon Z-Schedule Z-Polish A-Reply | There are 2 places were we compute if a message can be replied or not:
- In the `ActionListPresenter`, [here](https://github.com/vector-im/element-x-android/blob/develop/features/messages/impl/src/main/kotlin/io/element/android/features/messages/impl/actionlist/ActionListPresenter.kt#L100), for the action displayed ... | 1.0 | Reply action: harmonize condition - There are 2 places were we compute if a message can be replied or not:
- In the `ActionListPresenter`, [here](https://github.com/vector-im/element-x-android/blob/develop/features/messages/impl/src/main/kotlin/io/element/android/features/messages/impl/actionlist/ActionListPresenter... | defect | reply action harmonize condition there are places were we compute if a message can be replied or not in the actionlistpresenter for the action displayed when long pressing on an event and in the timelinepresenter as a global boolean for the timeline to enable or not the swipe gesture to tr... | 1 |
3,656 | 6,537,310,443 | IssuesEvent | 2017-08-31 21:49:58 | TerraME/terrame | https://api.github.com/repos/TerraME/terrame | closed | CellularSpace:geometry = true as default? | <No Backward Compatibility> Core task | It is necessary to load `CellularSpace` with `geometry = true` to compute GPM and also to use `Cell:area()`. What about set its default value as `true` and the user that wants to save memory set it to `false`? | True | CellularSpace:geometry = true as default? - It is necessary to load `CellularSpace` with `geometry = true` to compute GPM and also to use `Cell:area()`. What about set its default value as `true` and the user that wants to save memory set it to `false`? | non_defect | cellularspace geometry true as default it is necessary to load cellularspace with geometry true to compute gpm and also to use cell area what about set its default value as true and the user that wants to save memory set it to false | 0 |
80,149 | 9,983,430,328 | IssuesEvent | 2019-07-10 12:24:38 | mhmdtshref/portfolio | https://api.github.com/repos/mhmdtshref/portfolio | opened | Figma: Create admin app main page | design | Should create a Figma design for the main page of the admin app. | 1.0 | Figma: Create admin app main page - Should create a Figma design for the main page of the admin app. | non_defect | figma create admin app main page should create a figma design for the main page of the admin app | 0 |
68,574 | 21,715,236,167 | IssuesEvent | 2022-05-10 17:13:23 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | opened | The hover state of pills is low contrast and difficult to read | T-Defect | ### Steps to reproduce
1. Hover over a pill
2. Notice that the background becomes light, which makes the white text difficult to read
### Outcome
#### What did you expect?
To not have to :eyes:
#### What happened instead?

--- | :---
Nosy | @loewis, @ericvw, @haubi, @skrah, @aixtools, @miss-islington, @kadler, @isidentical
PRs | <li>python/cpython#682</li><li>python/cpython#21997</li><li>python/cpython#22001</li><li>python/cpython#22002</li>
Files | <li>[python-tip-aix-parallel.patch](htt... | 1.0 | Parallel build race condition on AIX since python-2.7 - BPO | [19521](https://bugs.python.org/issue19521)
--- | :---
Nosy | @loewis, @ericvw, @haubi, @skrah, @aixtools, @miss-islington, @kadler, @isidentical
PRs | <li>python/cpython#682</li><li>python/cpython#21997</li><li>python/cpython#22001</li><li>python/cpython#22... | non_defect | parallel build race condition on aix since python bpo nosy loewis ericvw haubi skrah aixtools miss islington kadler isidentical prs python cpython python cpython python cpython python cpython files uploaded as text plain at by haubi fix para... | 0 |
81,013 | 30,658,770,057 | IssuesEvent | 2023-07-25 13:48:06 | SeleniumHQ/selenium | https://api.github.com/repos/SeleniumHQ/selenium | closed | [🐛 Bug]: Unable to obtain driver using Selenium Manager | R-awaiting answer I-defect | ### What happened?
C:\Users\<username>\AppData\Local\Temp\selenium-manager4780040182003919112691930970461\selenium-manager.exe
Script is unable to obtain driver. Though the selenium-manager.exe is available on above path. Below highlight error is shown.
I ran maven clean command, updated the project with latest ja... | 1.0 | [🐛 Bug]: Unable to obtain driver using Selenium Manager - ### What happened?
C:\Users\<username>\AppData\Local\Temp\selenium-manager4780040182003919112691930970461\selenium-manager.exe
Script is unable to obtain driver. Though the selenium-manager.exe is available on above path. Below highlight error is shown.
I... | defect | unable to obtain driver using selenium manager what happened c users appdata local temp selenium selenium manager exe script is unable to obtain driver though the selenium manager exe is available on above path below highlight error is shown i ran maven clean command updated the project with la... | 1 |
154,787 | 13,577,344,188 | IssuesEvent | 2020-09-20 00:40:55 | holtzmak/Humane-Transport | https://api.github.com/repos/holtzmak/Humane-Transport | opened | Add "Adobe XD vs Figma" Wiki page | documentation | Add a page to the wiki where it will discuss the pros and cons about the UI/UX tools. After the comparison, we will decide which one to use | 1.0 | Add "Adobe XD vs Figma" Wiki page - Add a page to the wiki where it will discuss the pros and cons about the UI/UX tools. After the comparison, we will decide which one to use | non_defect | add adobe xd vs figma wiki page add a page to the wiki where it will discuss the pros and cons about the ui ux tools after the comparison we will decide which one to use | 0 |
75,366 | 9,222,950,823 | IssuesEvent | 2019-03-12 01:12:03 | prysmaticlabs/prysm | https://api.github.com/repos/prysmaticlabs/prysm | closed | p2p: Implement PeerInfo and Send to Single Peer | Needs Design | [Design doc](https://docs.google.com/document/d/1cthKuGPreOSQH96Ujt7sArcT-IRICk6b-QcdD0EnLsI/edit)
- [ ] Add details to peer info based on requirements by the underlying p2p protocol
- [ ] Implement `func (s *Server) Send(msg interface{}, peer Peer)`
More details to come through the design. | 1.0 | p2p: Implement PeerInfo and Send to Single Peer - [Design doc](https://docs.google.com/document/d/1cthKuGPreOSQH96Ujt7sArcT-IRICk6b-QcdD0EnLsI/edit)
- [ ] Add details to peer info based on requirements by the underlying p2p protocol
- [ ] Implement `func (s *Server) Send(msg interface{}, peer Peer)`
More deta... | non_defect | implement peerinfo and send to single peer add details to peer info based on requirements by the underlying protocol implement func s server send msg interface peer peer more details to come through the design | 0 |
175,766 | 13,608,865,967 | IssuesEvent | 2020-09-23 03:35:02 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | kv/kvclient/kvcoord: TestTxnCoordSenderRetries failed | C-test-failure O-robot branch-master | [(kv/kvclient/kvcoord).TestTxnCoordSenderRetries failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2174486&tab=buildLog) on [master@09bb6460c0ed1a882db95472e2d962dd57a80aaf](https://github.com/cockroachdb/cockroach/commits/09bb6460c0ed1a882db95472e2d962dd57a80aaf):
```
=== RUN TestTxnCoordSenderRetries
-... | 1.0 | kv/kvclient/kvcoord: TestTxnCoordSenderRetries failed - [(kv/kvclient/kvcoord).TestTxnCoordSenderRetries failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2174486&tab=buildLog) on [master@09bb6460c0ed1a882db95472e2d962dd57a80aaf](https://github.com/cockroachdb/cockroach/commits/09bb6460c0ed1a882db95472e2d96... | non_defect | kv kvclient kvcoord testtxncoordsenderretries failed on run testtxncoordsenderretries fail testtxncoordsenderretries test log scope go test logs captured to go src github com cockroachdb cockroach artifacts test log scope go use show logs to present logs inline ru... | 0 |
306,143 | 26,439,453,515 | IssuesEvent | 2023-01-15 19:56:57 | sundarnagarajan/python_protected_class | https://api.github.com/repos/sundarnagarajan/python_protected_class | opened | Create separate test script for PY3-only tests | Tests | - Test case wrapping async context manager
- __aenter__, __aexit__
- See [link](https://www.educative.io/answers/what-is-the-asynchronous-context-manager-in-python)
- Test case wrapping coroutine
- 'send', 'throw', close' | 1.0 | Create separate test script for PY3-only tests - - Test case wrapping async context manager
- __aenter__, __aexit__
- See [link](https://www.educative.io/answers/what-is-the-asynchronous-context-manager-in-python)
- Test case wrapping coroutine
- 'send', 'throw', close' | non_defect | create separate test script for only tests test case wrapping async context manager aenter aexit see test case wrapping coroutine send throw close | 0 |
58,643 | 16,671,045,824 | IssuesEvent | 2021-06-07 10:54:36 | primefaces/primeng | https://api.github.com/repos/primefaces/primeng | closed | Button icon css class not set after it has been initialized | defect | **I'm submitting a ...**
```
[x] bug report => Search github for a similar issue or PR before submitting
[ ] feature request => Please check if request is not on the roadmap already https://github.com/primefaces/primeng/wiki/Roadmap
[ ] support request => Please do not submit support request here, instead see http:... | 1.0 | Button icon css class not set after it has been initialized - **I'm submitting a ...**
```
[x] bug report => Search github for a similar issue or PR before submitting
[ ] feature request => Please check if request is not on the roadmap already https://github.com/primefaces/primeng/wiki/Roadmap
[ ] support request =... | defect | button icon css class not set after it has been initialized i m submitting a bug report search github for a similar issue or pr before submitting feature request please check if request is not on the roadmap already support request please do not submit support request here instead se... | 1 |
41,248 | 10,343,662,323 | IssuesEvent | 2019-09-04 09:26:05 | cakephp/cakephp | https://api.github.com/repos/cakephp/cakephp | opened | 4.x: Plugin path resolution wrong for templates | defect | This is a (multiple allowed):
* [x] bug
4.x
### What you did
bin/cake dto generate
I tried the Dto plugin in a 4.x app, it errored on the twig file to be found:
The following paths were searched:
```
- /.../cake4.local/templates/Dto/
- /.../cake4.local/vendor/dereuromark/cakephp-dto/src/Template... | 1.0 | 4.x: Plugin path resolution wrong for templates - This is a (multiple allowed):
* [x] bug
4.x
### What you did
bin/cake dto generate
I tried the Dto plugin in a 4.x app, it errored on the twig file to be found:
The following paths were searched:
```
- /.../cake4.local/templates/Dto/
- /.../cake4... | defect | x plugin path resolution wrong for templates this is a multiple allowed bug x what you did bin cake dto generate i tried the dto plugin in a x app it errored on the twig file to be found the following paths were searched local templates dto local ven... | 1 |
73,929 | 24,868,778,914 | IssuesEvent | 2022-10-27 13:52:04 | SeleniumHQ/selenium | https://api.github.com/repos/SeleniumHQ/selenium | opened | [🐛 Bug]: Unsupported Operation Exception For Getting Default Value From A Disabled Select Box | I-defect needs-triaging | ### What happened?
[🐛 Bug]: Unsupported Operation Exception For Getting Default Value From A Disabled Select Box
Getting
java.lang.UnsupportedOperationException: Select element is disabled and may not be used.
### How can we reproduce the issue?
```shell
when trying to fetch default value by calling ".getF... | 1.0 | [🐛 Bug]: Unsupported Operation Exception For Getting Default Value From A Disabled Select Box - ### What happened?
[🐛 Bug]: Unsupported Operation Exception For Getting Default Value From A Disabled Select Box
Getting
java.lang.UnsupportedOperationException: Select element is disabled and may not be used.
#... | defect | unsupported operation exception for getting default value from a disabled select box what happened unsupported operation exception for getting default value from a disabled select box getting java lang unsupportedoperationexception select element is disabled and may not be used how can we ... | 1 |
77,624 | 9,603,407,634 | IssuesEvent | 2019-05-10 16:58:45 | infor-design/design-system | https://api.github.com/repos/infor-design/design-system | closed | Add dark and contrast variants for uplift theme | for: design | - [x] Uplift dark variant
- [x] Uplift high-contrast variant | 1.0 | Add dark and contrast variants for uplift theme - - [x] Uplift dark variant
- [x] Uplift high-contrast variant | non_defect | add dark and contrast variants for uplift theme uplift dark variant uplift high contrast variant | 0 |
27,623 | 5,060,707,963 | IssuesEvent | 2016-12-22 13:05:20 | OlafvdSpek/xbt | https://api.github.com/repos/OlafvdSpek/xbt | closed | GitHub | auto-migrated Priority-Medium Type-Defect | ```
Let`s go to GitHub
I create https://github.com/poiuty/xbt
I give access rights to this repository.
```
Original issue reported on code.google.com by `df3434er...@gmail.com` on 14 Jul 2015 at 7:03
| 1.0 | GitHub - ```
Let`s go to GitHub
I create https://github.com/poiuty/xbt
I give access rights to this repository.
```
Original issue reported on code.google.com by `df3434er...@gmail.com` on 14 Jul 2015 at 7:03
| defect | github let s go to github i create i give access rights to this repository original issue reported on code google com by gmail com on jul at | 1 |
31,428 | 5,951,103,473 | IssuesEvent | 2017-05-26 18:33:51 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | /refout and /debug together should be an error | Area-Compilers Documentation | But we have a test that asserts it is OK:
``` c#
var outWriter = new StringWriter(CultureInfo.InvariantCulture);
var csc = new MockCSharpCompiler(null, dir.Path,
new[] { "/nologo", "/out:a.dll", "/refonly", "/debug", "/deterministic", "/doc:doc.xml", "a.cs" });
... | 1.0 | /refout and /debug together should be an error - But we have a test that asserts it is OK:
``` c#
var outWriter = new StringWriter(CultureInfo.InvariantCulture);
var csc = new MockCSharpCompiler(null, dir.Path,
new[] { "/nologo", "/out:a.dll", "/refonly", "/debug", "/determ... | non_defect | refout and debug together should be an error but we have a test that asserts it is ok c var outwriter new stringwriter cultureinfo invariantculture var csc new mockcsharpcompiler null dir path new nologo out a dll refonly debug determi... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.