Unnamed: 0
int64 0
832k
| id
float64 2.49B
32.1B
| type
stringclasses 1
value | created_at
stringlengths 19
19
| repo
stringlengths 5
112
| repo_url
stringlengths 34
141
| action
stringclasses 3
values | title
stringlengths 1
757
| labels
stringlengths 4
664
| body
stringlengths 3
261k
| index
stringclasses 10
values | text_combine
stringlengths 96
261k
| label
stringclasses 2
values | text
stringlengths 96
232k
| binary_label
int64 0
1
|
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
220,385
| 17,191,905,863
|
IssuesEvent
|
2021-07-16 12:15:27
|
elastic/kibana
|
https://api.github.com/repos/elastic/kibana
|
closed
|
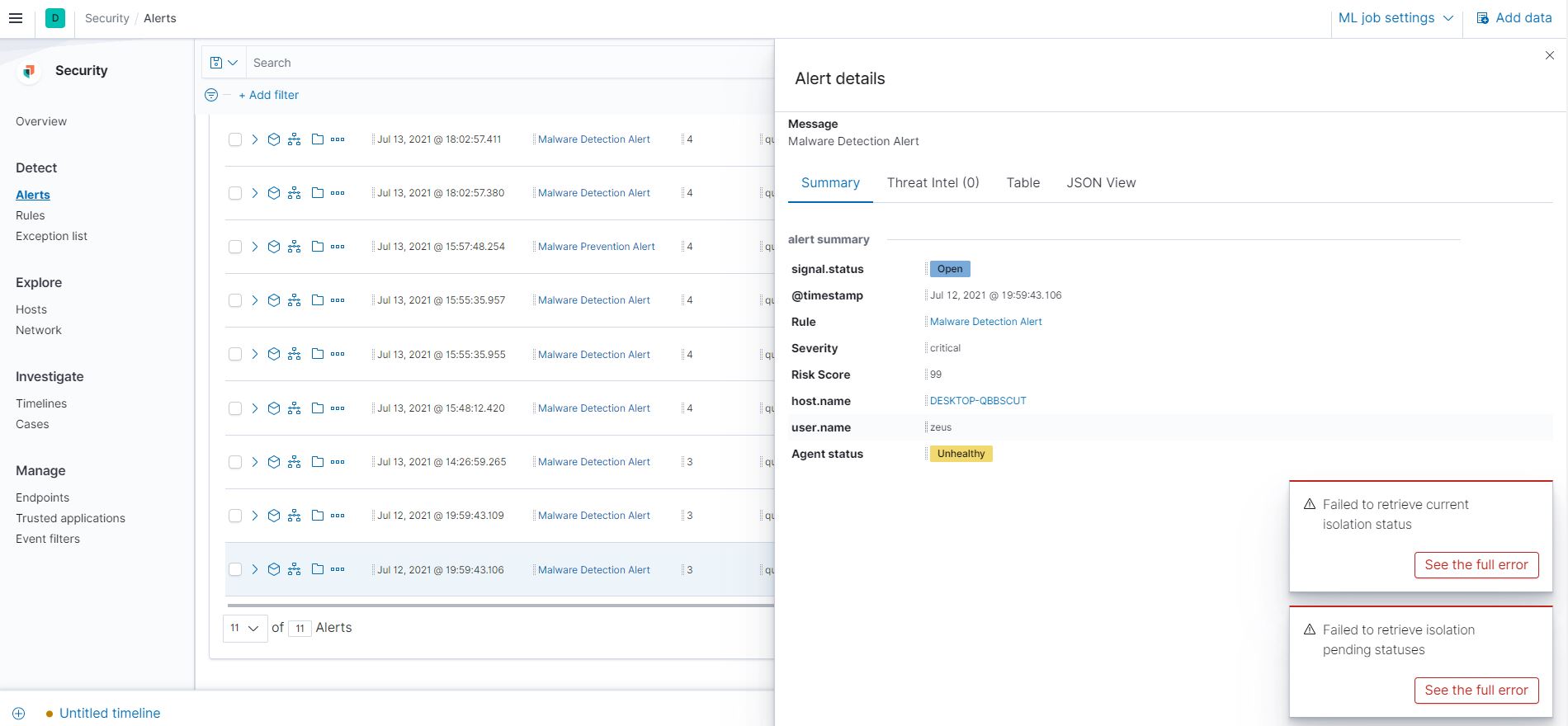
[Security Solution] For gold license, we get error messages for host isolation in alert details flyout
|
7.14.0 QA:Ready for Testing Team: SecuritySolution Team:Onboarding and Lifecycle Mgt bug impact:high
|
**Describe the feature**
For gold license, we get error messages for host isolation in alert details flyout
**Build Details:**
```
VERSION: 7.14.0 BC2
BUILD: 42401
COMMIT: 9826a943dc2e47f26ec6de94816e7d297b752994
ARTIFACT: https://staging.elastic.co/7.14.0-e99135ef/summary-7.14.0.html
```
**Preconditions**
1. Elastic 7.14.0 environment should be deployed.
2. Get a gold license
**Steps to Reproduce**
1. Navigate to the Alerts Tab
2. Click on the '>' icon for an endpoint alert
3. Observe the error notification pop-ups for the isolation status that starts showing up.
**Test data**
N/A
**Impacted Test case(s)**
N/A
**Actual Result**
For gold license, we get error messages for host isolation in alert details flyout
**Expected Result**
For gold license, we should not get error messages for host isolation in alert details flyout
**What's Working**
N/A
**What's Not Working**
N/A
**Screen Recording**
**Logs**:
N/A
|
1.0
|
[Security Solution] For gold license, we get error messages for host isolation in alert details flyout - **Describe the feature**
For gold license, we get error messages for host isolation in alert details flyout
**Build Details:**
```
VERSION: 7.14.0 BC2
BUILD: 42401
COMMIT: 9826a943dc2e47f26ec6de94816e7d297b752994
ARTIFACT: https://staging.elastic.co/7.14.0-e99135ef/summary-7.14.0.html
```
**Preconditions**
1. Elastic 7.14.0 environment should be deployed.
2. Get a gold license
**Steps to Reproduce**
1. Navigate to the Alerts Tab
2. Click on the '>' icon for an endpoint alert
3. Observe the error notification pop-ups for the isolation status that starts showing up.
**Test data**
N/A
**Impacted Test case(s)**
N/A
**Actual Result**
For gold license, we get error messages for host isolation in alert details flyout
**Expected Result**
For gold license, we should not get error messages for host isolation in alert details flyout
**What's Working**
N/A
**What's Not Working**
N/A
**Screen Recording**
**Logs**:
N/A
|
non_defect
|
for gold license we get error messages for host isolation in alert details flyout describe the feature for gold license we get error messages for host isolation in alert details flyout build details version build commit artifact preconditions elastic environment should be deployed get a gold license steps to reproduce navigate to the alerts tab click on the icon for an endpoint alert observe the error notification pop ups for the isolation status that starts showing up test data n a impacted test case s n a actual result for gold license we get error messages for host isolation in alert details flyout expected result for gold license we should not get error messages for host isolation in alert details flyout what s working n a what s not working n a screen recording logs n a
| 0
|
79,015
| 15,586,093,802
|
IssuesEvent
|
2021-03-18 01:09:31
|
mibo32/fitbit-api-example-java
|
https://api.github.com/repos/mibo32/fitbit-api-example-java
|
opened
|
CVE-2020-36184 (High) detected in jackson-databind-2.8.1.jar
|
security vulnerability
|
## CVE-2020-36184 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.1.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: fitbit-api-example-java/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.4.0.RELEASE.jar (Root Library)
- :x: **jackson-databind-2.8.1.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.tomcat.dbcp.dbcp2.datasources.PerUserPoolDataSource.
<p>Publish Date: 2021-01-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36184>CVE-2020-36184</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2998">https://github.com/FasterXML/jackson-databind/issues/2998</a></p>
<p>Release Date: 2021-01-06</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2020-36184 (High) detected in jackson-databind-2.8.1.jar - ## CVE-2020-36184 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.1.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: fitbit-api-example-java/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.4.0.RELEASE.jar (Root Library)
- :x: **jackson-databind-2.8.1.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.tomcat.dbcp.dbcp2.datasources.PerUserPoolDataSource.
<p>Publish Date: 2021-01-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36184>CVE-2020-36184</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2998">https://github.com/FasterXML/jackson-databind/issues/2998</a></p>
<p>Release Date: 2021-01-06</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file fitbit api example java pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy spring boot starter web release jar root library x jackson databind jar vulnerable library vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache tomcat dbcp datasources peruserpooldatasource publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with whitesource
| 0
|
792,252
| 27,952,644,414
|
IssuesEvent
|
2023-03-24 10:01:32
|
visual-framework/vf-core
|
https://api.github.com/repos/visual-framework/vf-core
|
closed
|
Angular compatibility support for vf-banner component
|
Priority: Medium Type: Feature Type: Compatibility
|
Currently, we only have Nunjucks and HTML support for each component. This ticket is created to make [vf-banner](https://stable.visual-framework.dev/components/vf-banner/index.html) component with [Angular](https://angular.io/) support format.
This should support all variants of `vf-banner` and other supporting parameters as given in the documentation.
- [x] Make sure it will work for Angular projects and update the document to which angular version it will support
- [x] Make sure it supports all varients and parameters as it is working now in HTML & Nunjucks version
- [x] Test these angular changes in a plain angular project locally and see if everything works
|
1.0
|
Angular compatibility support for vf-banner component - Currently, we only have Nunjucks and HTML support for each component. This ticket is created to make [vf-banner](https://stable.visual-framework.dev/components/vf-banner/index.html) component with [Angular](https://angular.io/) support format.
This should support all variants of `vf-banner` and other supporting parameters as given in the documentation.
- [x] Make sure it will work for Angular projects and update the document to which angular version it will support
- [x] Make sure it supports all varients and parameters as it is working now in HTML & Nunjucks version
- [x] Test these angular changes in a plain angular project locally and see if everything works
|
non_defect
|
angular compatibility support for vf banner component currently we only have nunjucks and html support for each component this ticket is created to make component with support format this should support all variants of vf banner and other supporting parameters as given in the documentation make sure it will work for angular projects and update the document to which angular version it will support make sure it supports all varients and parameters as it is working now in html nunjucks version test these angular changes in a plain angular project locally and see if everything works
| 0
|
215,680
| 24,196,472,348
|
IssuesEvent
|
2022-09-24 01:02:57
|
ChoeMinji/redis-6.2.3
|
https://api.github.com/repos/ChoeMinji/redis-6.2.3
|
opened
|
CVE-2022-35951 (High) detected in redis6.2.6
|
security vulnerability
|
## CVE-2022-35951 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>redis6.2.6</b></p></summary>
<p>
<p>Redis is an in-memory database that persists on disk. The data model is key-value, but many different kind of values are supported: Strings, Lists, Sets, Sorted Sets, Hashes, Streams, HyperLogLogs, Bitmaps.</p>
<p>Library home page: <a href=https://github.com/redis/redis.git>https://github.com/redis/redis.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/src/t_stream.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Redis is an in-memory database that persists on disk. Versions 7.0.0 and above, prior to 7.0.5 are vulnerable to an Integer Overflow. Executing an `XAUTOCLAIM` command on a stream key in a specific state, with a specially crafted `COUNT` argument may cause an integer overflow, a subsequent heap overflow, and potentially lead to remote code execution. This has been patched in Redis version 7.0.5. No known workarounds exist.
<p>Publish Date: 2022-09-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-35951>CVE-2022-35951</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/redis/redis/security/advisories/GHSA-5gc4-76rx-22c9">https://github.com/redis/redis/security/advisories/GHSA-5gc4-76rx-22c9</a></p>
<p>Release Date: 2022-09-23</p>
<p>Fix Resolution: 7.0.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2022-35951 (High) detected in redis6.2.6 - ## CVE-2022-35951 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>redis6.2.6</b></p></summary>
<p>
<p>Redis is an in-memory database that persists on disk. The data model is key-value, but many different kind of values are supported: Strings, Lists, Sets, Sorted Sets, Hashes, Streams, HyperLogLogs, Bitmaps.</p>
<p>Library home page: <a href=https://github.com/redis/redis.git>https://github.com/redis/redis.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/src/t_stream.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Redis is an in-memory database that persists on disk. Versions 7.0.0 and above, prior to 7.0.5 are vulnerable to an Integer Overflow. Executing an `XAUTOCLAIM` command on a stream key in a specific state, with a specially crafted `COUNT` argument may cause an integer overflow, a subsequent heap overflow, and potentially lead to remote code execution. This has been patched in Redis version 7.0.5. No known workarounds exist.
<p>Publish Date: 2022-09-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-35951>CVE-2022-35951</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/redis/redis/security/advisories/GHSA-5gc4-76rx-22c9">https://github.com/redis/redis/security/advisories/GHSA-5gc4-76rx-22c9</a></p>
<p>Release Date: 2022-09-23</p>
<p>Fix Resolution: 7.0.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve high detected in cve high severity vulnerability vulnerable library redis is an in memory database that persists on disk the data model is key value but many different kind of values are supported strings lists sets sorted sets hashes streams hyperloglogs bitmaps library home page a href found in base branch master vulnerable source files src t stream c vulnerability details redis is an in memory database that persists on disk versions and above prior to are vulnerable to an integer overflow executing an xautoclaim command on a stream key in a specific state with a specially crafted count argument may cause an integer overflow a subsequent heap overflow and potentially lead to remote code execution this has been patched in redis version no known workarounds exist publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend
| 0
|
31,875
| 6,652,430,459
|
IssuesEvent
|
2017-09-29 01:23:49
|
enforcer574/smashclub
|
https://api.github.com/repos/enforcer574/smashclub
|
opened
|
Duplicate event signups
|
Defect Incident Priority 3
|
Players are sometimes signing up for the same event twice. Invesigate a way to prevent this from happening.
|
1.0
|
Duplicate event signups - Players are sometimes signing up for the same event twice. Invesigate a way to prevent this from happening.
|
defect
|
duplicate event signups players are sometimes signing up for the same event twice invesigate a way to prevent this from happening
| 1
|
17,693
| 3,012,930,109
|
IssuesEvent
|
2015-07-29 04:17:46
|
yawlfoundation/yawl
|
https://api.github.com/repos/yawlfoundation/yawl
|
closed
|
workitems are not removed for case started by the worklet service
|
auto-migrated Priority-Medium Type-Defect
|
```
What steps will reproduce the problem?
1. upload gynonc.xml and start a case (as data fill in once MRI)
2. complete the workitem for check examinations. The worklet service will
now start the radiology worklet. In admin queues you will see three new
workitems starting with radiology.
3. go to the cases tab and remove the gynonc case. The gynonc case as well
the radiology case is now removed.
4. go to admin queues. You will find there three workitems starting with
radiology. These should have been removed! It is possible to allocate these
workitems to a user by clicking on the start button. However, once done
this, they disappear.
What version of the product are you using? On what operating system?
The last version of YAWL provided at 28/10/2008. Operating system is
windows server 2003 with java 1.6
Please provide any additional information below.
I include gynonc.xml for the gynonc case. gynonc.xrs is the ruleset and
radiology.xml is the file for the radiology case.
```
Original issue reported on code.google.com by `Ronny.M...@gmail.com` on 29 Oct 2008 at 10:41
Attachments:
* [gynonc.xml](https://storage.googleapis.com/google-code-attachments/yawl/issue-202/comment-0/gynonc.xml)
* [radiology.xml](https://storage.googleapis.com/google-code-attachments/yawl/issue-202/comment-0/radiology.xml)
* [gynonc.xrs](https://storage.googleapis.com/google-code-attachments/yawl/issue-202/comment-0/gynonc.xrs)
|
1.0
|
workitems are not removed for case started by the worklet service - ```
What steps will reproduce the problem?
1. upload gynonc.xml and start a case (as data fill in once MRI)
2. complete the workitem for check examinations. The worklet service will
now start the radiology worklet. In admin queues you will see three new
workitems starting with radiology.
3. go to the cases tab and remove the gynonc case. The gynonc case as well
the radiology case is now removed.
4. go to admin queues. You will find there three workitems starting with
radiology. These should have been removed! It is possible to allocate these
workitems to a user by clicking on the start button. However, once done
this, they disappear.
What version of the product are you using? On what operating system?
The last version of YAWL provided at 28/10/2008. Operating system is
windows server 2003 with java 1.6
Please provide any additional information below.
I include gynonc.xml for the gynonc case. gynonc.xrs is the ruleset and
radiology.xml is the file for the radiology case.
```
Original issue reported on code.google.com by `Ronny.M...@gmail.com` on 29 Oct 2008 at 10:41
Attachments:
* [gynonc.xml](https://storage.googleapis.com/google-code-attachments/yawl/issue-202/comment-0/gynonc.xml)
* [radiology.xml](https://storage.googleapis.com/google-code-attachments/yawl/issue-202/comment-0/radiology.xml)
* [gynonc.xrs](https://storage.googleapis.com/google-code-attachments/yawl/issue-202/comment-0/gynonc.xrs)
|
defect
|
workitems are not removed for case started by the worklet service what steps will reproduce the problem upload gynonc xml and start a case as data fill in once mri complete the workitem for check examinations the worklet service will now start the radiology worklet in admin queues you will see three new workitems starting with radiology go to the cases tab and remove the gynonc case the gynonc case as well the radiology case is now removed go to admin queues you will find there three workitems starting with radiology these should have been removed it is possible to allocate these workitems to a user by clicking on the start button however once done this they disappear what version of the product are you using on what operating system the last version of yawl provided at operating system is windows server with java please provide any additional information below i include gynonc xml for the gynonc case gynonc xrs is the ruleset and radiology xml is the file for the radiology case original issue reported on code google com by ronny m gmail com on oct at attachments
| 1
|
32,718
| 6,901,824,862
|
IssuesEvent
|
2017-11-25 13:05:10
|
networkx/networkx
|
https://api.github.com/repos/networkx/networkx
|
closed
|
Possible syntax error in gml.py (readwrite)
|
Defect
|
https://github.com/networkx/networkx/blob/e3566e53793cdccc19a8c2ff9c056e0d7b524634/networkx/readwrite/gml.py#L680
I've got an error when I want to write a .gml file from a network using the write_gml() function. At line 680 there is "test" instead of "text" I think.
|
1.0
|
Possible syntax error in gml.py (readwrite) - https://github.com/networkx/networkx/blob/e3566e53793cdccc19a8c2ff9c056e0d7b524634/networkx/readwrite/gml.py#L680
I've got an error when I want to write a .gml file from a network using the write_gml() function. At line 680 there is "test" instead of "text" I think.
|
defect
|
possible syntax error in gml py readwrite i ve got an error when i want to write a gml file from a network using the write gml function at line there is test instead of text i think
| 1
|
18,612
| 3,075,317,014
|
IssuesEvent
|
2015-08-20 13:03:56
|
skaut/dsw-oddil
|
https://api.github.com/repos/skaut/dsw-oddil
|
opened
|
Theme check: slug šablony nesouhlasí s umístěním v adresáři
|
defect template
|
WARNING: Your theme appears to be in the wrong directory for the theme name. The directory name must match the slug of the theme. This theme's correct slug and text-domain is dobr%c3%bd-skautsk%c3%bd-web-odd%c3%adl.
|
1.0
|
Theme check: slug šablony nesouhlasí s umístěním v adresáři - WARNING: Your theme appears to be in the wrong directory for the theme name. The directory name must match the slug of the theme. This theme's correct slug and text-domain is dobr%c3%bd-skautsk%c3%bd-web-odd%c3%adl.
|
defect
|
theme check slug šablony nesouhlasí s umístěním v adresáři warning your theme appears to be in the wrong directory for the theme name the directory name must match the slug of the theme this theme s correct slug and text domain is dobr bd skautsk bd web odd adl
| 1
|
47
| 2,497,181,414
|
IssuesEvent
|
2015-01-07 02:20:23
|
cakephp/cakephp
|
https://api.github.com/repos/cakephp/cakephp
|
closed
|
3.0 - FixtureManager uncovered edge cases
|
Defect
|
```diff
diff --git a/tests/TestCase/TestSuite/FixtureManagerTest.php b/tests/TestCase/TestSuite/FixtureManagerTest.php
index 4b8c9b7..fafc201 100644
--- a/tests/TestCase/TestSuite/FixtureManagerTest.php
+++ b/tests/TestCase/TestSuite/FixtureManagerTest.php
@@ -72,4 +72,23 @@ class FixtureManagerTest extends TestCase
$fixtures['plugin.test_plugin.articles']
);
}
+
+ public function testFixturizeCustom()
+ {
+ $test = $this->getMock('Cake\TestSuite\TestCase');
+ $test->fixtures = ['custom.articles'];
+ $this->manager->fixturize($test);
+ $fixtures = $this->manager->loaded();
+ }
}
```
Fails:
```
..E
Time: 487 ms, Memory: 8.00Mb
There was 1 error:
1) Cake\Test\TestSuite\FixtureManagerTest::testFixturizeCustom
Undefined variable: baseNamespace
/Users/jad/Projects/Contrib/cake/src/TestSuite/Fixture/FixtureManager.php:164
```
Another one that fails hard (undefined offset) is with plugins that use vendor name, like gourmet/faker (i.e. `$fixtures = 'plugin.gourmet/faker.articles'`). I had to use: `plugin.gourmet/faker/articles` for it to work.
|
1.0
|
3.0 - FixtureManager uncovered edge cases -
```diff
diff --git a/tests/TestCase/TestSuite/FixtureManagerTest.php b/tests/TestCase/TestSuite/FixtureManagerTest.php
index 4b8c9b7..fafc201 100644
--- a/tests/TestCase/TestSuite/FixtureManagerTest.php
+++ b/tests/TestCase/TestSuite/FixtureManagerTest.php
@@ -72,4 +72,23 @@ class FixtureManagerTest extends TestCase
$fixtures['plugin.test_plugin.articles']
);
}
+
+ public function testFixturizeCustom()
+ {
+ $test = $this->getMock('Cake\TestSuite\TestCase');
+ $test->fixtures = ['custom.articles'];
+ $this->manager->fixturize($test);
+ $fixtures = $this->manager->loaded();
+ }
}
```
Fails:
```
..E
Time: 487 ms, Memory: 8.00Mb
There was 1 error:
1) Cake\Test\TestSuite\FixtureManagerTest::testFixturizeCustom
Undefined variable: baseNamespace
/Users/jad/Projects/Contrib/cake/src/TestSuite/Fixture/FixtureManager.php:164
```
Another one that fails hard (undefined offset) is with plugins that use vendor name, like gourmet/faker (i.e. `$fixtures = 'plugin.gourmet/faker.articles'`). I had to use: `plugin.gourmet/faker/articles` for it to work.
|
defect
|
fixturemanager uncovered edge cases diff diff git a tests testcase testsuite fixturemanagertest php b tests testcase testsuite fixturemanagertest php index a tests testcase testsuite fixturemanagertest php b tests testcase testsuite fixturemanagertest php class fixturemanagertest extends testcase fixtures public function testfixturizecustom test this getmock cake testsuite testcase test fixtures this manager fixturize test fixtures this manager loaded fails e time ms memory there was error cake test testsuite fixturemanagertest testfixturizecustom undefined variable basenamespace users jad projects contrib cake src testsuite fixture fixturemanager php another one that fails hard undefined offset is with plugins that use vendor name like gourmet faker i e fixtures plugin gourmet faker articles i had to use plugin gourmet faker articles for it to work
| 1
|
73,702
| 24,761,290,846
|
IssuesEvent
|
2022-10-22 00:59:59
|
networkx/networkx
|
https://api.github.com/repos/networkx/networkx
|
closed
|
`connectionstyle` argument of `nx.draw_networkx_edges()` does not work properly for multigraphs and undirected graphs
|
Defect Visualization
|
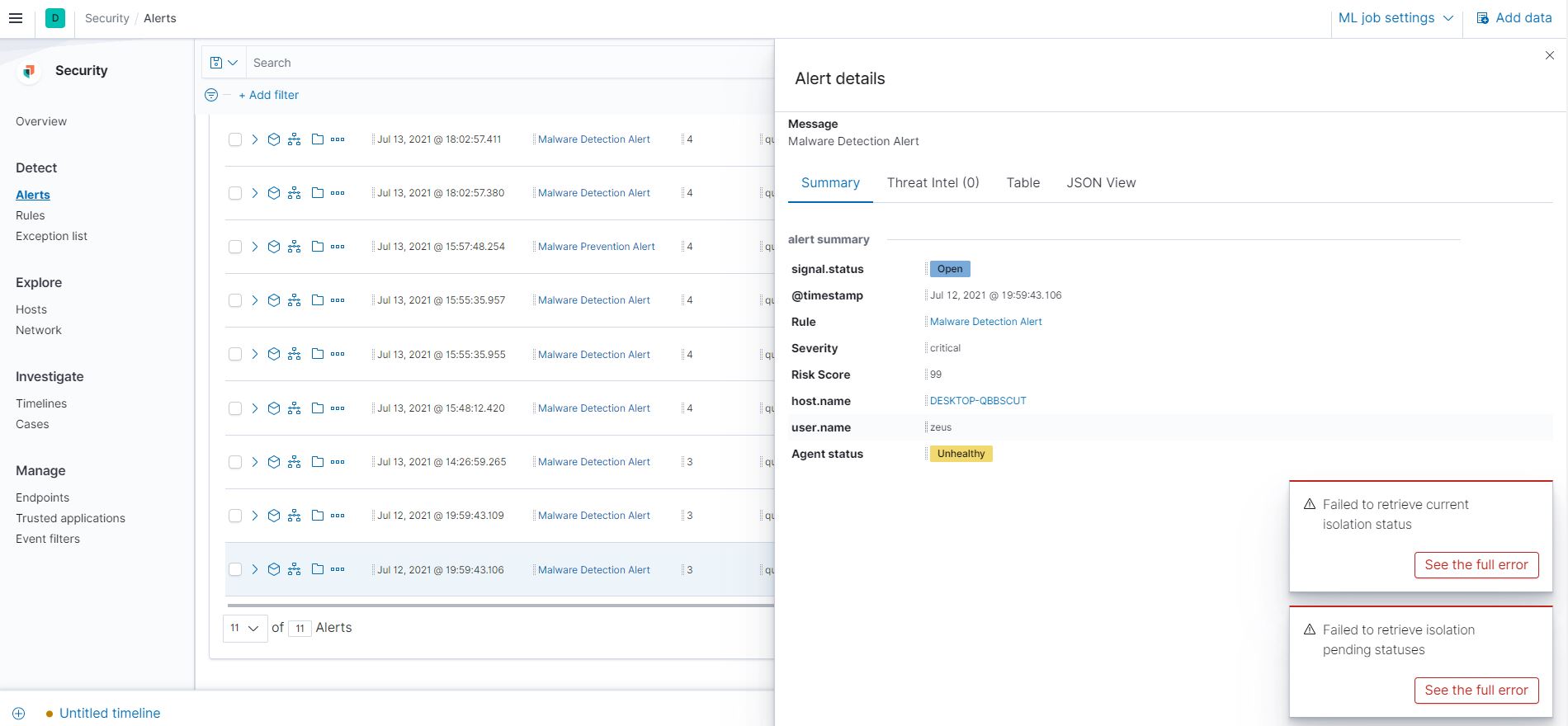
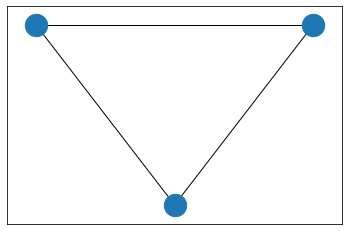
`connectionstyle` argument of `nx.draw_networkx_edges()` does not work properly for MultiGraphs and Undirected graphs. Consider the following example:
```
G=nx.DiGraph([(1,2),(3,1),(3,2)])
positions = {1:(0,0),2:(1,-2), 3:(2,0)}
nx.draw_networkx_nodes(G, pos=positions, node_size = 500)
nx.draw_networkx_edges(G, pos=positions, arrowstyle="-", connectionstyle="arc3,rad=0.3");
```
Output is the following:
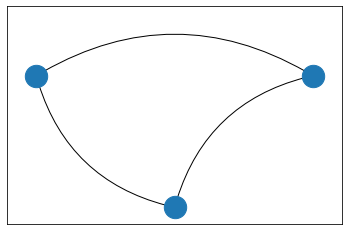
The outputs of the same code snippet when G is created as a multigraph and an undirected graph (`G=nx.MultiGraph([(1,2),(3,1),(3,2)])` and `G=nx.Graph([(1,2),(3,1),(3,2)])`) as follows:
|
1.0
|
`connectionstyle` argument of `nx.draw_networkx_edges()` does not work properly for multigraphs and undirected graphs - `connectionstyle` argument of `nx.draw_networkx_edges()` does not work properly for MultiGraphs and Undirected graphs. Consider the following example:
```
G=nx.DiGraph([(1,2),(3,1),(3,2)])
positions = {1:(0,0),2:(1,-2), 3:(2,0)}
nx.draw_networkx_nodes(G, pos=positions, node_size = 500)
nx.draw_networkx_edges(G, pos=positions, arrowstyle="-", connectionstyle="arc3,rad=0.3");
```
Output is the following:
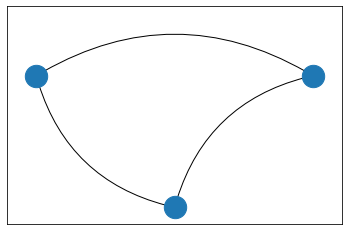
The outputs of the same code snippet when G is created as a multigraph and an undirected graph (`G=nx.MultiGraph([(1,2),(3,1),(3,2)])` and `G=nx.Graph([(1,2),(3,1),(3,2)])`) as follows:
|
defect
|
connectionstyle argument of nx draw networkx edges does not work properly for multigraphs and undirected graphs connectionstyle argument of nx draw networkx edges does not work properly for multigraphs and undirected graphs consider the following example g nx digraph positions nx draw networkx nodes g pos positions node size nx draw networkx edges g pos positions arrowstyle connectionstyle rad output is the following the outputs of the same code snippet when g is created as a multigraph and an undirected graph g nx multigraph and g nx graph as follows
| 1
|
46,273
| 13,055,883,088
|
IssuesEvent
|
2020-07-30 03:01:00
|
icecube-trac/tix2
|
https://api.github.com/repos/icecube-trac/tix2
|
opened
|
dataio - dataio-pyshovel Popup allow all keys (Trac #900)
|
Incomplete Migration Migrated from Trac combo core defect
|
Migrated from https://code.icecube.wisc.edu/ticket/900
```json
{
"status": "closed",
"changetime": "2019-01-11T21:45:56",
"description": "Certain keys are being intercepted in the Popup class (particularly j and k). This is likely an interaction between the global keybindings and Edit.keypress(). A likely fix will involve modifying self._command_map and removing the letters (make sure to copy it before editing, since it is by default a reference to the global keybindings).",
"reporter": "david.schultz",
"cc": "",
"resolution": "fixed",
"_ts": "1547243156161165",
"component": "combo core",
"summary": "dataio - dataio-pyshovel Popup allow all keys",
"priority": "major",
"keywords": "dataio-pyshovel",
"time": "2015-03-12T05:12:27",
"milestone": "",
"owner": "olivas",
"type": "defect"
}
```
|
1.0
|
dataio - dataio-pyshovel Popup allow all keys (Trac #900) - Migrated from https://code.icecube.wisc.edu/ticket/900
```json
{
"status": "closed",
"changetime": "2019-01-11T21:45:56",
"description": "Certain keys are being intercepted in the Popup class (particularly j and k). This is likely an interaction between the global keybindings and Edit.keypress(). A likely fix will involve modifying self._command_map and removing the letters (make sure to copy it before editing, since it is by default a reference to the global keybindings).",
"reporter": "david.schultz",
"cc": "",
"resolution": "fixed",
"_ts": "1547243156161165",
"component": "combo core",
"summary": "dataio - dataio-pyshovel Popup allow all keys",
"priority": "major",
"keywords": "dataio-pyshovel",
"time": "2015-03-12T05:12:27",
"milestone": "",
"owner": "olivas",
"type": "defect"
}
```
|
defect
|
dataio dataio pyshovel popup allow all keys trac migrated from json status closed changetime description certain keys are being intercepted in the popup class particularly j and k this is likely an interaction between the global keybindings and edit keypress a likely fix will involve modifying self command map and removing the letters make sure to copy it before editing since it is by default a reference to the global keybindings reporter david schultz cc resolution fixed ts component combo core summary dataio dataio pyshovel popup allow all keys priority major keywords dataio pyshovel time milestone owner olivas type defect
| 1
|
52,213
| 13,211,407,853
|
IssuesEvent
|
2020-08-15 22:55:43
|
icecube-trac/tix4
|
https://api.github.com/repos/icecube-trac/tix4
|
opened
|
improvedLinefit in EHE filter (L1 online and L2) (Trac #1858)
|
Incomplete Migration Migrated from Trac combo reconstruction defect
|
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/1858">https://code.icecube.wisc.edu/projects/icecube/ticket/1858</a>, reported by claudio.kopperand owned by david.schultz</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:13:18",
"_ts": "1550067198646291",
"description": "It seems that the EHE filter uses the various sub-modules of improvedLinefit separately (both in the online EHE filter and in L2). Since the change to merge all improvedLinefit modules into the linefit module and merging them into a single module these scripts in L2 are currently broken.\n\nI would suggest to restore improvedLinefit for now so that these scripts are usable again (linefit does not need to be changed). This would be a short-term fix. In the slightly longer term we should just provide the original sub-modules in linefit.\n\nThis currently blocks a potential pass2 reprocessing.",
"reporter": "claudio.kopper",
"cc": "",
"resolution": "fixed",
"time": "2016-09-12T14:57:04",
"component": "combo reconstruction",
"summary": "improvedLinefit in EHE filter (L1 online and L2)",
"priority": "blocker",
"keywords": "",
"milestone": "",
"owner": "david.schultz",
"type": "defect"
}
```
</p>
</details>
|
1.0
|
improvedLinefit in EHE filter (L1 online and L2) (Trac #1858) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/1858">https://code.icecube.wisc.edu/projects/icecube/ticket/1858</a>, reported by claudio.kopperand owned by david.schultz</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:13:18",
"_ts": "1550067198646291",
"description": "It seems that the EHE filter uses the various sub-modules of improvedLinefit separately (both in the online EHE filter and in L2). Since the change to merge all improvedLinefit modules into the linefit module and merging them into a single module these scripts in L2 are currently broken.\n\nI would suggest to restore improvedLinefit for now so that these scripts are usable again (linefit does not need to be changed). This would be a short-term fix. In the slightly longer term we should just provide the original sub-modules in linefit.\n\nThis currently blocks a potential pass2 reprocessing.",
"reporter": "claudio.kopper",
"cc": "",
"resolution": "fixed",
"time": "2016-09-12T14:57:04",
"component": "combo reconstruction",
"summary": "improvedLinefit in EHE filter (L1 online and L2)",
"priority": "blocker",
"keywords": "",
"milestone": "",
"owner": "david.schultz",
"type": "defect"
}
```
</p>
</details>
|
defect
|
improvedlinefit in ehe filter online and trac migrated from json status closed changetime ts description it seems that the ehe filter uses the various sub modules of improvedlinefit separately both in the online ehe filter and in since the change to merge all improvedlinefit modules into the linefit module and merging them into a single module these scripts in are currently broken n ni would suggest to restore improvedlinefit for now so that these scripts are usable again linefit does not need to be changed this would be a short term fix in the slightly longer term we should just provide the original sub modules in linefit n nthis currently blocks a potential reprocessing reporter claudio kopper cc resolution fixed time component combo reconstruction summary improvedlinefit in ehe filter online and priority blocker keywords milestone owner david schultz type defect
| 1
|
79,561
| 28,375,113,659
|
IssuesEvent
|
2023-04-12 20:10:30
|
JohnAustinDev/xulsword
|
https://api.github.com/repos/JohnAustinDev/xulsword
|
closed
|
Add GUI capability to display the Greek TR words in module KJV version 2.6 lemma markup
|
Type-Defect Priority-Medium auto-migrated
|
```
From kjv.conf
SwordVersionDate=2014-02-15
Version=2.6
History_2.6=Fixed bugs. Added Greek from TR.
Example: (mod2imp)
$$$Matthew 1:1
<w lemma="strong:G976 lemma.TR:βιβλος" morph="robinson:N-NSF" src="1">The
book</w> <w lemma="strong:G1078 lemma.TR:γενεσεως"
morph="robinson:N-GSF" src="2">of the generation</w> <w lemma="strong:G2424
lemma.TR:ιησου" morph="robinson:N-GSM" src="3">of Jesus</w> <w
lemma="strong:G5547 lemma.TR:χριστου" morph="robinson:N-GSM"
src="4">Christ</w>, <w lemma="strong:G5207 lemma.TR:υιου"
morph="robinson:N-GSM" src="5">the son</w> <w lemma="strong:G1138
lemma.TR:δαβιδ" morph="robinson:N-PRI" src="6">of David</w>, <w
lemma="strong:G5207 lemma.TR:υιου" morph="robinson:N-GSM" src="7">the
son</w> <w lemma="strong:G11 lemma.TR:αβρααμ" morph="robinson:N-PRI"
src="8">of Abraham</w>.
```
Original issue reported on code.google.com by `DFH...@gmail.com` on 16 Feb 2014 at 3:36
|
1.0
|
Add GUI capability to display the Greek TR words in module KJV version 2.6 lemma markup - ```
From kjv.conf
SwordVersionDate=2014-02-15
Version=2.6
History_2.6=Fixed bugs. Added Greek from TR.
Example: (mod2imp)
$$$Matthew 1:1
<w lemma="strong:G976 lemma.TR:βιβλος" morph="robinson:N-NSF" src="1">The
book</w> <w lemma="strong:G1078 lemma.TR:γενεσεως"
morph="robinson:N-GSF" src="2">of the generation</w> <w lemma="strong:G2424
lemma.TR:ιησου" morph="robinson:N-GSM" src="3">of Jesus</w> <w
lemma="strong:G5547 lemma.TR:χριστου" morph="robinson:N-GSM"
src="4">Christ</w>, <w lemma="strong:G5207 lemma.TR:υιου"
morph="robinson:N-GSM" src="5">the son</w> <w lemma="strong:G1138
lemma.TR:δαβιδ" morph="robinson:N-PRI" src="6">of David</w>, <w
lemma="strong:G5207 lemma.TR:υιου" morph="robinson:N-GSM" src="7">the
son</w> <w lemma="strong:G11 lemma.TR:αβρααμ" morph="robinson:N-PRI"
src="8">of Abraham</w>.
```
Original issue reported on code.google.com by `DFH...@gmail.com` on 16 Feb 2014 at 3:36
|
defect
|
add gui capability to display the greek tr words in module kjv version lemma markup from kjv conf swordversiondate version history fixed bugs added greek from tr example matthew the book w lemma strong lemma tr γενεσεως morph robinson n gsf src of the generation w lemma strong lemma tr ιησου morph robinson n gsm src of jesus w lemma strong lemma tr χριστου morph robinson n gsm src christ w lemma strong lemma tr υιου morph robinson n gsm src the son w lemma strong lemma tr δαβιδ morph robinson n pri src of david w lemma strong lemma tr υιου morph robinson n gsm src the son w lemma strong lemma tr αβρααμ morph robinson n pri src of abraham original issue reported on code google com by dfh gmail com on feb at
| 1
|
313,788
| 9,576,057,826
|
IssuesEvent
|
2019-05-07 08:11:24
|
code-ready/crc
|
https://api.github.com/repos/code-ready/crc
|
closed
|
Panic during `Creating VM` when minimum amount of memory can not be allocated
|
kind/enhancement os/linux priority/major size/S
|
I run `./crc start -b ../crc_libvirt_v4.1.0.rc0.tar.xz` on my Hyper-V Fedora 29 VM with bundle downloaded and got:
```
[jeffmaury@localhost crc-0.85.0-linux-amd64]$ ./crc start -b ../crc_libvirt_v4.1.0.rc0.tar.xz
crc - Local OpenShift 4.x cluster
INFO Checking if Virtualization is enabled
INFO Checking if KVM is enabled
INFO Checking if Libvirt is installed
INFO Checking if user is part of libvirt group
INFO Checking if Libvirt is enabled
INFO Checking if Libvirt daemon is running
INFO Checking if crc-driver-libvirt is installed
INFO Checking if Libvirt crc network is available
INFO Checking if Libvirt crc network is active
INFO Checking if /etc/NetworkManager/dnsmasq.d/crc.conf exists
INFO Extracting the Bundle tarball ...
INFO Creating VM ...
ERRO Error occured: Error creating the VM. [Error creating machine: Error in driver during machine creation: virError(Code=9, Domain=20, Message='operation failed: domain 'crc' already exists with uuid aa2e9019-19d0-4bb7-99b5-5442917016dc')]
ERRO Error creating host: Error creating the VM. Error creating machine: Error in driver during machine creation: virError(Code=9, Domain=20, Message='operation failed: domain 'crc' already exists with uuid aa2e9019-19d0-4bb7-99b5-5442917016dc')
panic: runtime error: invalid memory address or nil pointer dereference
[signal SIGSEGV: segmentation violation code=0x1 addr=0x8 pc=0x7d989f]
goroutine 1 [running]:
github.com/code-ready/crc/pkg/crc/machine.Start(0x993283, 0x3, 0x7ffe8c55a8b2, 0x20, 0x9961af, 0x7, 0x2000, 0x4, 0x0, 0x0, ...)
/home/prkumar/work/github/crc/pkg/crc/machine/machine.go:83 +0x12cf
github.com/code-ready/crc/cmd/crc/cmd.runStart(0xc00000d600, 0x0, 0x2)
/home/prkumar/work/github/crc/cmd/crc/cmd/start.go:52 +0x1bc
github.com/code-ready/crc/cmd/crc/cmd.glob..func6(0xdb3b00, 0xc00000d600, 0x0, 0x2)
/home/prkumar/work/github/crc/cmd/crc/cmd/start.go:25 +0x3f
github.com/spf13/cobra.(*Command).execute(0xdb3b00, 0xc00000d5c0, 0x2, 0x2, 0xdb3b00, 0xc00000d5c0)
/home/prkumar/work/go/pkg/mod/github.com/spf13/cobra@v0.0.3/command.go:766 +0x2cc
github.com/spf13/cobra.(*Command).ExecuteC(0xdb3640, 0xdb3fc0, 0xc00019bf68, 0xc00019bf88)
/home/prkumar/work/go/pkg/mod/github.com/spf13/cobra@v0.0.3/command.go:852 +0x2fd
github.com/spf13/cobra.(*Command).Execute(0xdb3640, 0x1, 0xdb3fc0)
/home/prkumar/work/go/pkg/mod/github.com/spf13/cobra@v0.0.3/command.go:800 +0x2b
github.com/code-ready/crc/cmd/crc/cmd.Execute()
/home/prkumar/work/github/crc/cmd/crc/cmd/root.go:59 +0x2d
main.main()
/home/prkumar/work/github/crc/cmd/crc/main.go:8 +0x20
[jeffmaury@localhost crc-0.85.0-linux-amd64]$
```
|
1.0
|
Panic during `Creating VM` when minimum amount of memory can not be allocated - I run `./crc start -b ../crc_libvirt_v4.1.0.rc0.tar.xz` on my Hyper-V Fedora 29 VM with bundle downloaded and got:
```
[jeffmaury@localhost crc-0.85.0-linux-amd64]$ ./crc start -b ../crc_libvirt_v4.1.0.rc0.tar.xz
crc - Local OpenShift 4.x cluster
INFO Checking if Virtualization is enabled
INFO Checking if KVM is enabled
INFO Checking if Libvirt is installed
INFO Checking if user is part of libvirt group
INFO Checking if Libvirt is enabled
INFO Checking if Libvirt daemon is running
INFO Checking if crc-driver-libvirt is installed
INFO Checking if Libvirt crc network is available
INFO Checking if Libvirt crc network is active
INFO Checking if /etc/NetworkManager/dnsmasq.d/crc.conf exists
INFO Extracting the Bundle tarball ...
INFO Creating VM ...
ERRO Error occured: Error creating the VM. [Error creating machine: Error in driver during machine creation: virError(Code=9, Domain=20, Message='operation failed: domain 'crc' already exists with uuid aa2e9019-19d0-4bb7-99b5-5442917016dc')]
ERRO Error creating host: Error creating the VM. Error creating machine: Error in driver during machine creation: virError(Code=9, Domain=20, Message='operation failed: domain 'crc' already exists with uuid aa2e9019-19d0-4bb7-99b5-5442917016dc')
panic: runtime error: invalid memory address or nil pointer dereference
[signal SIGSEGV: segmentation violation code=0x1 addr=0x8 pc=0x7d989f]
goroutine 1 [running]:
github.com/code-ready/crc/pkg/crc/machine.Start(0x993283, 0x3, 0x7ffe8c55a8b2, 0x20, 0x9961af, 0x7, 0x2000, 0x4, 0x0, 0x0, ...)
/home/prkumar/work/github/crc/pkg/crc/machine/machine.go:83 +0x12cf
github.com/code-ready/crc/cmd/crc/cmd.runStart(0xc00000d600, 0x0, 0x2)
/home/prkumar/work/github/crc/cmd/crc/cmd/start.go:52 +0x1bc
github.com/code-ready/crc/cmd/crc/cmd.glob..func6(0xdb3b00, 0xc00000d600, 0x0, 0x2)
/home/prkumar/work/github/crc/cmd/crc/cmd/start.go:25 +0x3f
github.com/spf13/cobra.(*Command).execute(0xdb3b00, 0xc00000d5c0, 0x2, 0x2, 0xdb3b00, 0xc00000d5c0)
/home/prkumar/work/go/pkg/mod/github.com/spf13/cobra@v0.0.3/command.go:766 +0x2cc
github.com/spf13/cobra.(*Command).ExecuteC(0xdb3640, 0xdb3fc0, 0xc00019bf68, 0xc00019bf88)
/home/prkumar/work/go/pkg/mod/github.com/spf13/cobra@v0.0.3/command.go:852 +0x2fd
github.com/spf13/cobra.(*Command).Execute(0xdb3640, 0x1, 0xdb3fc0)
/home/prkumar/work/go/pkg/mod/github.com/spf13/cobra@v0.0.3/command.go:800 +0x2b
github.com/code-ready/crc/cmd/crc/cmd.Execute()
/home/prkumar/work/github/crc/cmd/crc/cmd/root.go:59 +0x2d
main.main()
/home/prkumar/work/github/crc/cmd/crc/main.go:8 +0x20
[jeffmaury@localhost crc-0.85.0-linux-amd64]$
```
|
non_defect
|
panic during creating vm when minimum amount of memory can not be allocated i run crc start b crc libvirt tar xz on my hyper v fedora vm with bundle downloaded and got crc start b crc libvirt tar xz crc local openshift x cluster info checking if virtualization is enabled info checking if kvm is enabled info checking if libvirt is installed info checking if user is part of libvirt group info checking if libvirt is enabled info checking if libvirt daemon is running info checking if crc driver libvirt is installed info checking if libvirt crc network is available info checking if libvirt crc network is active info checking if etc networkmanager dnsmasq d crc conf exists info extracting the bundle tarball info creating vm erro error occured error creating the vm erro error creating host error creating the vm error creating machine error in driver during machine creation virerror code domain message operation failed domain crc already exists with uuid panic runtime error invalid memory address or nil pointer dereference goroutine github com code ready crc pkg crc machine start home prkumar work github crc pkg crc machine machine go github com code ready crc cmd crc cmd runstart home prkumar work github crc cmd crc cmd start go github com code ready crc cmd crc cmd glob home prkumar work github crc cmd crc cmd start go github com cobra command execute home prkumar work go pkg mod github com cobra command go github com cobra command executec home prkumar work go pkg mod github com cobra command go github com cobra command execute home prkumar work go pkg mod github com cobra command go github com code ready crc cmd crc cmd execute home prkumar work github crc cmd crc cmd root go main main home prkumar work github crc cmd crc main go
| 0
|
20,966
| 16,374,666,674
|
IssuesEvent
|
2021-05-15 21:17:49
|
godotengine/godot
|
https://api.github.com/repos/godotengine/godot
|
closed
|
Add option to copy path/name/value of setting
|
enhancement topic:editor usability
|
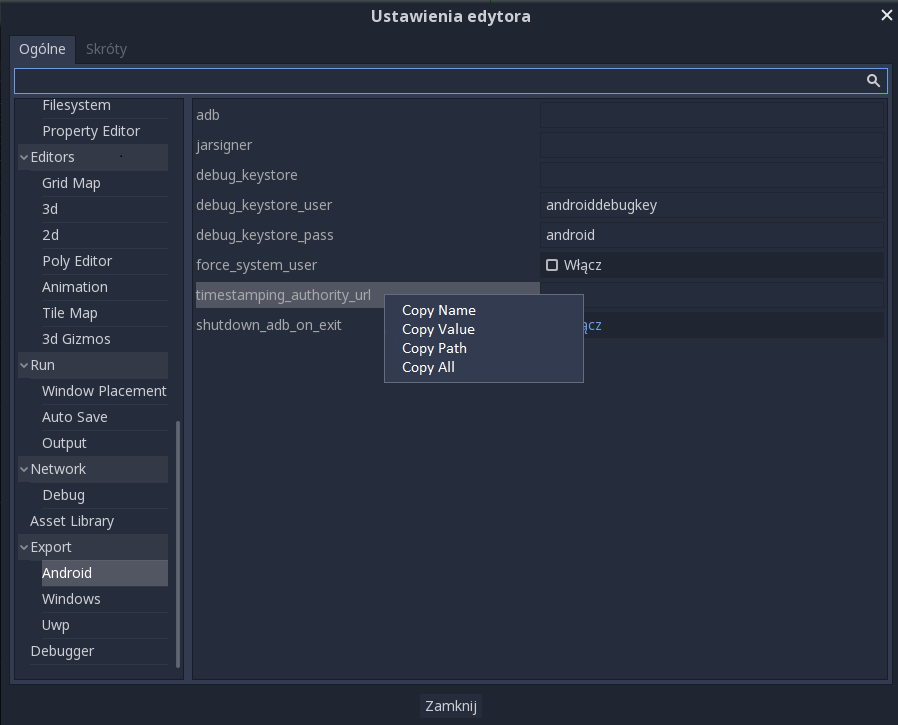
**Godot version:**
3.1 calinou c4e75aa
**OS/device including version:**
Windows 10
**Issue description:**
It would be nice if in settings(both Editor and Project) would be option to copy things by right-clicking, because it is possible to do mistake when rewrite it.
I think there should be 4 options:
Copy name - Copy only name of setting e.g. **timestamping_authority_url**
Copy value - Copy only value of setting e.g. **true** or for colours **#ff22aa**
Copy path - Copy path e.g. **Export/Android/jarsigner**
Copy all - Copy path and value e.g. **Export/Android/jarsigner -> #ff22aa**
|
True
|
Add option to copy path/name/value of setting - **Godot version:**
3.1 calinou c4e75aa
**OS/device including version:**
Windows 10
**Issue description:**
It would be nice if in settings(both Editor and Project) would be option to copy things by right-clicking, because it is possible to do mistake when rewrite it.
I think there should be 4 options:
Copy name - Copy only name of setting e.g. **timestamping_authority_url**
Copy value - Copy only value of setting e.g. **true** or for colours **#ff22aa**
Copy path - Copy path e.g. **Export/Android/jarsigner**
Copy all - Copy path and value e.g. **Export/Android/jarsigner -> #ff22aa**
|
non_defect
|
add option to copy path name value of setting godot version calinou os device including version windows issue description it would be nice if in settings both editor and project would be option to copy things by right clicking because it is possible to do mistake when rewrite it i think there should be options copy name copy only name of setting e g timestamping authority url copy value copy only value of setting e g true or for colours copy path copy path e g export android jarsigner copy all copy path and value e g export android jarsigner
| 0
|
820,746
| 30,786,446,667
|
IssuesEvent
|
2023-07-31 13:32:11
|
googleapis/nodejs-storage
|
https://api.github.com/repos/googleapis/nodejs-storage
|
closed
|
The build failed
|
type: bug priority: p2 api: storage flakybot: issue flakybot: flaky
|
This test failed!
To configure my behavior, see [the Flaky Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/main/packages/flakybot).
If I'm commenting on this issue too often, add the `flakybot: quiet` label and
I will stop commenting.
---
commit: 1756827215773965006ac32e1dd92f1e583d24a9
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/dd83e92b-8adb-41a2-bb08-b7c5d768572b), [Sponge](http://sponge2/dd83e92b-8adb-41a2-bb08-b7c5d768572b)
status: failed
<details><summary>Test output</summary><br><pre>expected '' to match /Bucket nodejs-storage-samples-29d36e81-8096-4401-946a-6c39c26c06ea-a is now publicly readable/
AssertionError: expected '' to match /Bucket nodejs-storage-samples-29d36e81-8096-4401-946a-6c39c26c06ea-a is now publicly readable/
at Context.<anonymous> (system-test/buckets.test.js:342:10)
at processImmediate (internal/timers.js:464:21)</pre></details>
|
1.0
|
The build failed - This test failed!
To configure my behavior, see [the Flaky Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/main/packages/flakybot).
If I'm commenting on this issue too often, add the `flakybot: quiet` label and
I will stop commenting.
---
commit: 1756827215773965006ac32e1dd92f1e583d24a9
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/dd83e92b-8adb-41a2-bb08-b7c5d768572b), [Sponge](http://sponge2/dd83e92b-8adb-41a2-bb08-b7c5d768572b)
status: failed
<details><summary>Test output</summary><br><pre>expected '' to match /Bucket nodejs-storage-samples-29d36e81-8096-4401-946a-6c39c26c06ea-a is now publicly readable/
AssertionError: expected '' to match /Bucket nodejs-storage-samples-29d36e81-8096-4401-946a-6c39c26c06ea-a is now publicly readable/
at Context.<anonymous> (system-test/buckets.test.js:342:10)
at processImmediate (internal/timers.js:464:21)</pre></details>
|
non_defect
|
the build failed this test failed to configure my behavior see if i m commenting on this issue too often add the flakybot quiet label and i will stop commenting commit buildurl status failed test output expected to match bucket nodejs storage samples a is now publicly readable assertionerror expected to match bucket nodejs storage samples a is now publicly readable at context system test buckets test js at processimmediate internal timers js
| 0
|
134,705
| 5,232,869,302
|
IssuesEvent
|
2017-01-30 10:55:09
|
openvstorage/openvstorage-health-check
|
https://api.github.com/repos/openvstorage/openvstorage-health-check
|
closed
|
Output of healthcheck - json
|
priority_urgent state_inprogress type_enhancement
|
Output should have 2 types of output:
* human readable (default)
* json format (e.g. --to-json like alba)
Note: unattended can be removed.
|
1.0
|
Output of healthcheck - json - Output should have 2 types of output:
* human readable (default)
* json format (e.g. --to-json like alba)
Note: unattended can be removed.
|
non_defect
|
output of healthcheck json output should have types of output human readable default json format e g to json like alba note unattended can be removed
| 0
|
44,936
| 12,474,712,933
|
IssuesEvent
|
2020-05-29 10:09:02
|
Optiboot/optiboot
|
https://api.github.com/repos/Optiboot/optiboot
|
closed
|
Many board-level targets are obsolete...
|
Priority-Medium Type-Defect auto-migrated
|
```
A lot of the board-level targets (lilypad, PRO series) seem to have been
defined in the early days of those boards' development, when they were still
using ATmega168 CPUs. Most of the current versions of those boards use
ATmega328p CPUs.
```
Original issue reported on code.google.com by `wes...@gmail.com` on 10 Mar 2013 at 9:55
|
1.0
|
Many board-level targets are obsolete... - ```
A lot of the board-level targets (lilypad, PRO series) seem to have been
defined in the early days of those boards' development, when they were still
using ATmega168 CPUs. Most of the current versions of those boards use
ATmega328p CPUs.
```
Original issue reported on code.google.com by `wes...@gmail.com` on 10 Mar 2013 at 9:55
|
defect
|
many board level targets are obsolete a lot of the board level targets lilypad pro series seem to have been defined in the early days of those boards development when they were still using cpus most of the current versions of those boards use cpus original issue reported on code google com by wes gmail com on mar at
| 1
|
444,650
| 31,117,449,227
|
IssuesEvent
|
2023-08-15 01:51:39
|
Thinkmill/keystatic
|
https://api.github.com/repos/Thinkmill/keystatic
|
opened
|
Better DX / documentation for the Document field
|
documentation enhancement
|
Our Document field is a bit obscure to get running successfully with, a few things we can do to improve it:
- [ ] Only include valid markdown formatting options when you're using [shorthand syntax](https://keystatic.com/docs/fields/document#usage-example)
- [ ] Document what the shorthand syntax expands into, and include an example of the **full** [reference of fields](https://docsmill.dev/npm/@keystatic/core@0.0.115#/.fields.document.FormattingConfig) that are available
- [ ] Explain that turning on other features will require custom tags in your MarkDoc rendering, ref #504
- [ ] Add dev example projects that show how to render the full set of formatting options, in Next.js (with Reader) and Astro (with Markdoc integration)
|
1.0
|
Better DX / documentation for the Document field - Our Document field is a bit obscure to get running successfully with, a few things we can do to improve it:
- [ ] Only include valid markdown formatting options when you're using [shorthand syntax](https://keystatic.com/docs/fields/document#usage-example)
- [ ] Document what the shorthand syntax expands into, and include an example of the **full** [reference of fields](https://docsmill.dev/npm/@keystatic/core@0.0.115#/.fields.document.FormattingConfig) that are available
- [ ] Explain that turning on other features will require custom tags in your MarkDoc rendering, ref #504
- [ ] Add dev example projects that show how to render the full set of formatting options, in Next.js (with Reader) and Astro (with Markdoc integration)
|
non_defect
|
better dx documentation for the document field our document field is a bit obscure to get running successfully with a few things we can do to improve it only include valid markdown formatting options when you re using document what the shorthand syntax expands into and include an example of the full that are available explain that turning on other features will require custom tags in your markdoc rendering ref add dev example projects that show how to render the full set of formatting options in next js with reader and astro with markdoc integration
| 0
|
195,199
| 22,295,743,296
|
IssuesEvent
|
2022-06-13 01:11:38
|
monch1962/docker-accessibility-check
|
https://api.github.com/repos/monch1962/docker-accessibility-check
|
opened
|
CVE-2022-25851 (High) detected in jpeg-js-0.4.3.tgz
|
security vulnerability
|
## CVE-2022-25851 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jpeg-js-0.4.3.tgz</b></p></summary>
<p>A pure javascript JPEG encoder and decoder</p>
<p>Library home page: <a href="https://registry.npmjs.org/jpeg-js/-/jpeg-js-0.4.3.tgz">https://registry.npmjs.org/jpeg-js/-/jpeg-js-0.4.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/jpeg-js/package.json</p>
<p>
Dependency Hierarchy:
- playwright-1.10.0.tgz (Root Library)
- :x: **jpeg-js-0.4.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/monch1962/docker-accessibility-check/commit/ee72b8b6c5613d7cd6fb7f1f7b70ba20bd8c6821">ee72b8b6c5613d7cd6fb7f1f7b70ba20bd8c6821</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package jpeg-js before 0.4.4 are vulnerable to Denial of Service (DoS) where a particular piece of input will cause to enter an infinite loop and never return.
<p>Publish Date: 2022-06-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-25851>CVE-2022-25851</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-06-10</p>
<p>Fix Resolution: jpeg-js - 0.4.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2022-25851 (High) detected in jpeg-js-0.4.3.tgz - ## CVE-2022-25851 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jpeg-js-0.4.3.tgz</b></p></summary>
<p>A pure javascript JPEG encoder and decoder</p>
<p>Library home page: <a href="https://registry.npmjs.org/jpeg-js/-/jpeg-js-0.4.3.tgz">https://registry.npmjs.org/jpeg-js/-/jpeg-js-0.4.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/jpeg-js/package.json</p>
<p>
Dependency Hierarchy:
- playwright-1.10.0.tgz (Root Library)
- :x: **jpeg-js-0.4.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/monch1962/docker-accessibility-check/commit/ee72b8b6c5613d7cd6fb7f1f7b70ba20bd8c6821">ee72b8b6c5613d7cd6fb7f1f7b70ba20bd8c6821</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package jpeg-js before 0.4.4 are vulnerable to Denial of Service (DoS) where a particular piece of input will cause to enter an infinite loop and never return.
<p>Publish Date: 2022-06-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-25851>CVE-2022-25851</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-06-10</p>
<p>Fix Resolution: jpeg-js - 0.4.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve high detected in jpeg js tgz cve high severity vulnerability vulnerable library jpeg js tgz a pure javascript jpeg encoder and decoder library home page a href path to dependency file package json path to vulnerable library node modules jpeg js package json dependency hierarchy playwright tgz root library x jpeg js tgz vulnerable library found in head commit a href found in base branch main vulnerability details the package jpeg js before are vulnerable to denial of service dos where a particular piece of input will cause to enter an infinite loop and never return publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution jpeg js step up your open source security game with mend
| 0
|
309,626
| 9,477,691,676
|
IssuesEvent
|
2019-04-19 19:34:54
|
richelbilderbeek/djog_unos_2018
|
https://api.github.com/repos/richelbilderbeek/djog_unos_2018
|
closed
|
Split up sfml_resources::get_tile_sprite
|
junior medium priority
|
**Is your feature request related to a problem? Please describe.**
There is a clear pattern in `sfml_resources::get_tile_sprite`:
```c++
sf::Texture &sfml_resources::get_tile_sprite(const tile &t) noexcept //!OCLINT too long, needs to be fixed
{
switch (t.get_type()) //!OCLINT too few branches for now
{
case tile_type::tundra:
if (t.get_width() > 100) {
assert(t.get_height() == 100.0);
return m_tundra_laying;
}
assert(t.get_width() == 100.0);
return m_tundra_standing;
case tile_type::beach:
if (t.get_width() > 100) {
return m_beach_laying;
}
return m_beach_standing;
case tile_type::water:
if (t.get_width() > 100) {
return m_water_laying;
}
return m_water_standing;
case tile_type::dunes:
if (t.get_width() > 100) {
return m_dunes_laying;
}
return m_dunes_standing;
case tile_type::hills:
if (t.get_width() > 100) {
return m_hills_laying;
}
return m_hills_standing;
default:
return m_empty_tile;
}
}
```
For each tile, first the `tile_type` is checked, then its orientation. Reversing this simplifies the code and makes it more readable.
**Describe the solution you'd like**
(note: I think 'portrait' is the more commonly used name for 'standing', 'landscape' for 'lying')
* [ ] Move code to these two new private member functions of `sfml_resources`:
```c++
sf::Texture &sfml_resources::get_tile_sprite_portrait(const tile_type t) noexcept //!OCLINT cannot be simpler
```
and
```c++
sf::Texture &sfml_resources::get_tile_sprite_landscape(const tile_type t) noexcept //!OCLINT cannot be simpler
```
* [ ] Call the new function from the existing code
```c++
sf::Texture &sfml_resources::get_tile_sprite(const tile &t) noexcept
{
if (t.get_width() > t.get_height()
{
return get_tile_sprite_landscape(t.get_type());
}
else
{
//There are no square tiles (yet?)
assert(t.get_width() < t.get_height()
return get_tile_sprite_portrait(t.get_type());
}
}
```
* [ ] Activate the test
```c++
//#define FIX_ISSUE_538
#ifdef FIX_ISSUE_538
// Can get the sprite of a tile type
{
assert(resources.get_tile_sprite_portrait(tile_type::grassland).getSize().x > 0);
assert(resources.get_tile_sprite_landscape(tile_type::grassland).getSize().x > 0);
}
#endif // FIX_ISSUE_538
```
Remove the preprocessor directives. If it compiles, you are done :+1:
**Describe alternatives you've considered**
None.
**Additional context**
None.
|
1.0
|
Split up sfml_resources::get_tile_sprite - **Is your feature request related to a problem? Please describe.**
There is a clear pattern in `sfml_resources::get_tile_sprite`:
```c++
sf::Texture &sfml_resources::get_tile_sprite(const tile &t) noexcept //!OCLINT too long, needs to be fixed
{
switch (t.get_type()) //!OCLINT too few branches for now
{
case tile_type::tundra:
if (t.get_width() > 100) {
assert(t.get_height() == 100.0);
return m_tundra_laying;
}
assert(t.get_width() == 100.0);
return m_tundra_standing;
case tile_type::beach:
if (t.get_width() > 100) {
return m_beach_laying;
}
return m_beach_standing;
case tile_type::water:
if (t.get_width() > 100) {
return m_water_laying;
}
return m_water_standing;
case tile_type::dunes:
if (t.get_width() > 100) {
return m_dunes_laying;
}
return m_dunes_standing;
case tile_type::hills:
if (t.get_width() > 100) {
return m_hills_laying;
}
return m_hills_standing;
default:
return m_empty_tile;
}
}
```
For each tile, first the `tile_type` is checked, then its orientation. Reversing this simplifies the code and makes it more readable.
**Describe the solution you'd like**
(note: I think 'portrait' is the more commonly used name for 'standing', 'landscape' for 'lying')
* [ ] Move code to these two new private member functions of `sfml_resources`:
```c++
sf::Texture &sfml_resources::get_tile_sprite_portrait(const tile_type t) noexcept //!OCLINT cannot be simpler
```
and
```c++
sf::Texture &sfml_resources::get_tile_sprite_landscape(const tile_type t) noexcept //!OCLINT cannot be simpler
```
* [ ] Call the new function from the existing code
```c++
sf::Texture &sfml_resources::get_tile_sprite(const tile &t) noexcept
{
if (t.get_width() > t.get_height()
{
return get_tile_sprite_landscape(t.get_type());
}
else
{
//There are no square tiles (yet?)
assert(t.get_width() < t.get_height()
return get_tile_sprite_portrait(t.get_type());
}
}
```
* [ ] Activate the test
```c++
//#define FIX_ISSUE_538
#ifdef FIX_ISSUE_538
// Can get the sprite of a tile type
{
assert(resources.get_tile_sprite_portrait(tile_type::grassland).getSize().x > 0);
assert(resources.get_tile_sprite_landscape(tile_type::grassland).getSize().x > 0);
}
#endif // FIX_ISSUE_538
```
Remove the preprocessor directives. If it compiles, you are done :+1:
**Describe alternatives you've considered**
None.
**Additional context**
None.
|
non_defect
|
split up sfml resources get tile sprite is your feature request related to a problem please describe there is a clear pattern in sfml resources get tile sprite c sf texture sfml resources get tile sprite const tile t noexcept oclint too long needs to be fixed switch t get type oclint too few branches for now case tile type tundra if t get width assert t get height return m tundra laying assert t get width return m tundra standing case tile type beach if t get width return m beach laying return m beach standing case tile type water if t get width return m water laying return m water standing case tile type dunes if t get width return m dunes laying return m dunes standing case tile type hills if t get width return m hills laying return m hills standing default return m empty tile for each tile first the tile type is checked then its orientation reversing this simplifies the code and makes it more readable describe the solution you d like note i think portrait is the more commonly used name for standing landscape for lying move code to these two new private member functions of sfml resources c sf texture sfml resources get tile sprite portrait const tile type t noexcept oclint cannot be simpler and c sf texture sfml resources get tile sprite landscape const tile type t noexcept oclint cannot be simpler call the new function from the existing code c sf texture sfml resources get tile sprite const tile t noexcept if t get width t get height return get tile sprite landscape t get type else there are no square tiles yet assert t get width t get height return get tile sprite portrait t get type activate the test c define fix issue ifdef fix issue can get the sprite of a tile type assert resources get tile sprite portrait tile type grassland getsize x assert resources get tile sprite landscape tile type grassland getsize x endif fix issue remove the preprocessor directives if it compiles you are done describe alternatives you ve considered none additional context none
| 0
|
71,696
| 23,763,527,823
|
IssuesEvent
|
2022-09-01 10:53:15
|
primefaces/primefaces
|
https://api.github.com/repos/primefaces/primefaces
|
closed
|
Migration guide: Inplace change not mentioned in 6.2->7.0 migration guide (also impacting user guide)
|
:lady_beetle: defect :bangbang: needs-triage
|
### Describe the bug
I found another annoying and undocumented change from PF 6.2 to 7.0 (in addition to #8892).
I'm following the migration guide at:
https://primefaces.github.io/primefaces/11_0_0/#/../migrationguide/7_0
However, I see no mention of the fact that `<p:inplace>`, when adding `save` and/or `cancel` ajax behaviors, now requires an `update="@this"` in order for the inplace to work correctly (i.e.: to return to output mode).
### Reproducer
```xml
<p:inplace label="Foo" editor="true">
<p:inputText />
<p:ajax event="cancel" global="false" />
</p:inplace>
```
Try to hit the "cancel" button: nothing happens.
### Expected behavior
Honestly I would expect the inplace `@this` update to be automatic, as it was before, since this is an intrinsic mechanism of the component. Or else, if you think it should not, this should be well documented. The same user guide at https://primefaces.github.io/primefaces/7_0/#/components/inplace?id=inplace uses the following example:
```xml
<p:inplace editor="true">
<p:ajax event="save" listener="#{inplaceBean.handleSave}" update="msgs" />
<h:inputText value="#{inplaceBean.text}" />
</p:inplace>
<p:growl id="msgs" />
```
which I can't make to work unless I add `@this` in the `update` attribute of the `<p:ajax>`.
So, either the documentation or the library is wrong.
This makes the migration from 6.2 to 7.0 harder indeed...
### PrimeFaces edition
Community
### PrimeFaces version
7.0
### Theme
_No response_
### JSF implementation
Mojarra
### JSF version
2.2
### Java version
11
### Browser(s)
Firefox 104, Chrome 105
|
1.0
|
Migration guide: Inplace change not mentioned in 6.2->7.0 migration guide (also impacting user guide) - ### Describe the bug
I found another annoying and undocumented change from PF 6.2 to 7.0 (in addition to #8892).
I'm following the migration guide at:
https://primefaces.github.io/primefaces/11_0_0/#/../migrationguide/7_0
However, I see no mention of the fact that `<p:inplace>`, when adding `save` and/or `cancel` ajax behaviors, now requires an `update="@this"` in order for the inplace to work correctly (i.e.: to return to output mode).
### Reproducer
```xml
<p:inplace label="Foo" editor="true">
<p:inputText />
<p:ajax event="cancel" global="false" />
</p:inplace>
```
Try to hit the "cancel" button: nothing happens.
### Expected behavior
Honestly I would expect the inplace `@this` update to be automatic, as it was before, since this is an intrinsic mechanism of the component. Or else, if you think it should not, this should be well documented. The same user guide at https://primefaces.github.io/primefaces/7_0/#/components/inplace?id=inplace uses the following example:
```xml
<p:inplace editor="true">
<p:ajax event="save" listener="#{inplaceBean.handleSave}" update="msgs" />
<h:inputText value="#{inplaceBean.text}" />
</p:inplace>
<p:growl id="msgs" />
```
which I can't make to work unless I add `@this` in the `update` attribute of the `<p:ajax>`.
So, either the documentation or the library is wrong.
This makes the migration from 6.2 to 7.0 harder indeed...
### PrimeFaces edition
Community
### PrimeFaces version
7.0
### Theme
_No response_
### JSF implementation
Mojarra
### JSF version
2.2
### Java version
11
### Browser(s)
Firefox 104, Chrome 105
|
defect
|
migration guide inplace change not mentioned in migration guide also impacting user guide describe the bug i found another annoying and undocumented change from pf to in addition to i m following the migration guide at however i see no mention of the fact that when adding save and or cancel ajax behaviors now requires an update this in order for the inplace to work correctly i e to return to output mode reproducer xml try to hit the cancel button nothing happens expected behavior honestly i would expect the inplace this update to be automatic as it was before since this is an intrinsic mechanism of the component or else if you think it should not this should be well documented the same user guide at uses the following example xml which i can t make to work unless i add this in the update attribute of the so either the documentation or the library is wrong this makes the migration from to harder indeed primefaces edition community primefaces version theme no response jsf implementation mojarra jsf version java version browser s firefox chrome
| 1
|
12,837
| 15,095,661,831
|
IssuesEvent
|
2021-02-07 12:03:00
|
FlowCrypt/flowcrypt-browser
|
https://api.github.com/repos/FlowCrypt/flowcrypt-browser
|
closed
|
WKD evaluate all received keys
|
PGP or S/MIME actionable compatibility
|
Currently, our client implementation only looks at the first received key.
It should at least look at all of them (WKD response may contain any amount of keys in it), and pick the first key that is usable for encryption. Spec https://tools.ietf.org/html/draft-koch-openpgp-webkey-service-10
Recommend to do after #3003
Later on we will follow up with #3018
|
True
|
WKD evaluate all received keys - Currently, our client implementation only looks at the first received key.
It should at least look at all of them (WKD response may contain any amount of keys in it), and pick the first key that is usable for encryption. Spec https://tools.ietf.org/html/draft-koch-openpgp-webkey-service-10
Recommend to do after #3003
Later on we will follow up with #3018
|
non_defect
|
wkd evaluate all received keys currently our client implementation only looks at the first received key it should at least look at all of them wkd response may contain any amount of keys in it and pick the first key that is usable for encryption spec recommend to do after later on we will follow up with
| 0
|
63,457
| 17,669,046,965
|
IssuesEvent
|
2021-08-23 01:23:37
|
DDCorkum/CTMod
|
https://api.github.com/repos/DDCorkum/CTMod
|
closed
|
ct Bar Mode: since patch 9.1.0 (retail) Macros works no more in bar 2
|
- Defect CT_BarMod
|
Hi since the latest patch (9.1.0) I can't activate the following macro I have in bar 2 by hotkey:
#showtooltip Himmlische Azurwolkenschlange
/wirken [button:1] Himmlische Azurwolkenschlange
/wirken [button:2] Teufelsfeuerfalke
/wirken [button:3] Mechanischer Holzextraktor
When I click on it with the mouse it works as usual, but the hotkey by keyboard does not work since the new patch.
If I put the same macro on bar 3 it works by hotkey/keyboard.
Would be really great if that works again. Sorry for my English I am from Austria :)
Thanks in advance and best regards Nina
|
1.0
|
ct Bar Mode: since patch 9.1.0 (retail) Macros works no more in bar 2 - Hi since the latest patch (9.1.0) I can't activate the following macro I have in bar 2 by hotkey:
#showtooltip Himmlische Azurwolkenschlange
/wirken [button:1] Himmlische Azurwolkenschlange
/wirken [button:2] Teufelsfeuerfalke
/wirken [button:3] Mechanischer Holzextraktor
When I click on it with the mouse it works as usual, but the hotkey by keyboard does not work since the new patch.
If I put the same macro on bar 3 it works by hotkey/keyboard.
Would be really great if that works again. Sorry for my English I am from Austria :)
Thanks in advance and best regards Nina
|
defect
|
ct bar mode since patch retail macros works no more in bar hi since the latest patch i can t activate the following macro i have in bar by hotkey showtooltip himmlische azurwolkenschlange wirken himmlische azurwolkenschlange wirken teufelsfeuerfalke wirken mechanischer holzextraktor when i click on it with the mouse it works as usual but the hotkey by keyboard does not work since the new patch if i put the same macro on bar it works by hotkey keyboard would be really great if that works again sorry for my english i am from austria thanks in advance and best regards nina
| 1
|
2,192
| 2,603,977,741
|
IssuesEvent
|
2015-02-24 19:01:57
|
chrsmith/nishazi6
|
https://api.github.com/repos/chrsmith/nishazi6
|
opened
|
沈阳沈阳疱疹病毒感染治疗
|
auto-migrated Priority-Medium Type-Defect
|
```
沈阳沈阳疱疹病毒感染治疗〓沈陽軍區政治部醫院性病〓TEL��
�024-31023308〓成立于1946年,68年專注于性傳播疾病的研究和治�
��。位于沈陽市沈河區二緯路32號。是一所與新中國同建立共�
��煌的歷史悠久、設備精良、技術權威、專家云集,是預防、
保健、醫療、科研康復為一體的綜合性醫院。是國家首批公��
�甲等部隊醫院、全國首批醫療規范定點單位,是第四軍醫大�
��、東南大學等知名高等院校的教學醫院。曾被中國人民解放
軍空軍后勤部衛生部評為衛生工作先進單位,先后兩次榮立��
�體二等功。
```
-----
Original issue reported on code.google.com by `q964105...@gmail.com` on 4 Jun 2014 at 8:29
|
1.0
|
沈阳沈阳疱疹病毒感染治疗 - ```
沈阳沈阳疱疹病毒感染治疗〓沈陽軍區政治部醫院性病〓TEL��
�024-31023308〓成立于1946年,68年專注于性傳播疾病的研究和治�
��。位于沈陽市沈河區二緯路32號。是一所與新中國同建立共�
��煌的歷史悠久、設備精良、技術權威、專家云集,是預防、
保健、醫療、科研康復為一體的綜合性醫院。是國家首批公��
�甲等部隊醫院、全國首批醫療規范定點單位,是第四軍醫大�
��、東南大學等知名高等院校的教學醫院。曾被中國人民解放
軍空軍后勤部衛生部評為衛生工作先進單位,先后兩次榮立��
�體二等功。
```
-----
Original issue reported on code.google.com by `q964105...@gmail.com` on 4 Jun 2014 at 8:29
|
defect
|
沈阳沈阳疱疹病毒感染治疗 沈阳沈阳疱疹病毒感染治疗〓沈陽軍區政治部醫院性病〓tel�� � 〓 , � ��。 。是一所與新中國同建立共� ��煌的歷史悠久、設備精良、技術權威、專家云集,是預防、 保健、醫療、科研康復為一體的綜合性醫院。是國家首批公�� �甲等部隊醫院、全國首批醫療規范定點單位,是第四軍醫大� ��、東南大學等知名高等院校的教學醫院。曾被中國人民解放 軍空軍后勤部衛生部評為衛生工作先進單位,先后兩次榮立�� �體二等功。 original issue reported on code google com by gmail com on jun at
| 1
|
40,376
| 9,976,169,120
|
IssuesEvent
|
2019-07-09 14:32:51
|
cf-convention/cf-conventions
|
https://api.github.com/repos/cf-convention/cf-conventions
|
opened
|
Update CONTRIBUTING to mention templates
|
defect
|
https://github.com/cf-convention/cf-conventions/blob/master/CONTRIBUTING.md says
> 4. Use labels on issues and pull requests. Contributions must be presented as enhancements, defects, or typos and labeled accordingly.
Once you click New Issue, you are brought to a page where you choose a template, and I think it's self-explanatory from there. Thus, I think point 4 should be removed from CONTRIBUTING.md.
|
1.0
|
Update CONTRIBUTING to mention templates - https://github.com/cf-convention/cf-conventions/blob/master/CONTRIBUTING.md says
> 4. Use labels on issues and pull requests. Contributions must be presented as enhancements, defects, or typos and labeled accordingly.
Once you click New Issue, you are brought to a page where you choose a template, and I think it's self-explanatory from there. Thus, I think point 4 should be removed from CONTRIBUTING.md.
|
defect
|
update contributing to mention templates says use labels on issues and pull requests contributions must be presented as enhancements defects or typos and labeled accordingly once you click new issue you are brought to a page where you choose a template and i think it s self explanatory from there thus i think point should be removed from contributing md
| 1
|
156,042
| 13,640,265,248
|
IssuesEvent
|
2020-09-25 12:28:46
|
chartjs/Chart.js
|
https://api.github.com/repos/chartjs/Chart.js
|
closed
|
dist folder missing from samples folder
|
type: documentation
|
Hi,
dist folder is apparently missing from samples folder..
|
1.0
|
dist folder missing from samples folder -
Hi,
dist folder is apparently missing from samples folder..
|
non_defect
|
dist folder missing from samples folder hi dist folder is apparently missing from samples folder
| 0
|
65,017
| 19,013,625,526
|
IssuesEvent
|
2021-11-23 12:05:32
|
primefaces/primefaces
|
https://api.github.com/repos/primefaces/primefaces
|
closed
|
DataTable filtering should also handle collections
|
defect
|
https://github.com/primefaces/primefaces/blob/83636668d75e5c69e3b2ebbebadb518ed3ebf84b/primefaces/src/main/java/org/primefaces/component/api/UITable.java#L220
This function should also set filterValue to null if filterValue is a collection or an iterable that is empty.
|
1.0
|
DataTable filtering should also handle collections - https://github.com/primefaces/primefaces/blob/83636668d75e5c69e3b2ebbebadb518ed3ebf84b/primefaces/src/main/java/org/primefaces/component/api/UITable.java#L220
This function should also set filterValue to null if filterValue is a collection or an iterable that is empty.
|
defect
|
datatable filtering should also handle collections this function should also set filtervalue to null if filtervalue is a collection or an iterable that is empty
| 1
|
76,850
| 26,629,422,660
|
IssuesEvent
|
2023-01-24 16:43:18
|
zealdocs/zeal
|
https://api.github.com/repos/zealdocs/zeal
|
closed
|
Hotkeys do not work on certain keyboard mappings...
|
type/defect platform/linux scope/ui
|
I recognized that several hotkeys do not work on my machine (arch linux, xorg-server 1.18.1). I even encountered a segfault. The problematic line is [`native = keycodes.data()[0];`](https://github.com/zealdocs/zeal/blob/master/src/3rdparty/qxtglobalshortcut/qxtglobalshortcut_x11.cpp#L129). When there is no keycode this will result in a segfault.
I debugged the code and realized that the keys reported by the nativeEventFilter are different from the ones that I wanted to be grabbed before via [`xcb_grab_key_checked`](https://github.com/zealdocs/zeal/blob/master/src/3rdparty/qxtglobalshortcut/qxtglobalshortcut_x11.cpp#L142). The reason why my hotkey has no effect, is that the key reported by the nativeEventFilter is the one in `keycodes.data()[1]`. keycodes.data()[0] is adiaeresis (german Ä). Now I know that after registering <kbd>Alt</kbd>+<kbd>Y</kbd>, I can open zeal by pressing <kbd>Alt</kbd>+<kbd>Ä</kbd>.
Well I printed my keycode mapping like this (xmodmap -pke does it as well)
``` cpp
for (int cc =0 ; cc<256; ++cc){
qDebug() << cc << XKeysymToString(xcb_key_symbols_get_keysym(xcbKeySymbols,cc,0))
<< XKeysymToString(xcb_key_symbols_get_keysym(xcbKeySymbols,cc,1))
<< XKeysymToString(xcb_key_symbols_get_keysym(xcbKeySymbols,cc,2))
<< XKeysymToString(xcb_key_symbols_get_keysym(xcbKeySymbols,cc,3))
<< XKeysymToString(xcb_key_symbols_get_keysym(xcbKeySymbols,cc,4))
<< XKeysymToString(xcb_key_symbols_get_keysym(xcbKeySymbols,cc,6))
<< XKeysymToString(xcb_key_symbols_get_keysym(xcbKeySymbols,cc,7))
<< XKeysymToString(xcb_key_symbols_get_keysym(xcbKeySymbols,cc,8));
}
```
which looks like this (snippet)
```
48 adiaeresis Adiaeresis y Y dead_circumflex at Greek_upsilon period
49 dead_circumflex degree dead_circumflex dead_caron U2032 U21BB U02DE dead_abovedot
50 Shift_L Shift_L Caps_Lock
51 numbersign apostrophe ISO_Level3_Shift rightsinglequotemark
52 y Y udiaeresis Udiaeresis guillemotright numbersign Escape
```
And, yes, keysym Y (keycode 52 on my keyboard) is listed in the mapping of keycode 48 ( keysym Ä on my keyboard)... I stopped here working on this. Well this stuff is boring and annoying. Even xcb itelf states
> At the moment, XCB implements only a basic and incomplete sets of keyboard functions. Therefore, it greatly restricts the usages of XCB in "real-world" applications and duplicate the efforts as most applications ported to XCB so far (such as Awesome Window Manager, VLC and others) have to write their own implementation, which is often incomplete and buggy as it is rather tricky to implement properly and entirely.
I wish nobody to have to do this again, so I want to ask, if you are willing to make some kind of qxt-community organization (or soimething like that, doesnt have to be qxt). Qxt has been discontinued and there are several projects that are maintaining qxtglobalshortcut on their own, e.g. CopyQ, zeal, albert (mine, partially). If we'd unite our effort we could have more stability for less effort.
I think of a separated library for hotkey handling, not even necessarily using Qt.
|
1.0
|
Hotkeys do not work on certain keyboard mappings... - I recognized that several hotkeys do not work on my machine (arch linux, xorg-server 1.18.1). I even encountered a segfault. The problematic line is [`native = keycodes.data()[0];`](https://github.com/zealdocs/zeal/blob/master/src/3rdparty/qxtglobalshortcut/qxtglobalshortcut_x11.cpp#L129). When there is no keycode this will result in a segfault.
I debugged the code and realized that the keys reported by the nativeEventFilter are different from the ones that I wanted to be grabbed before via [`xcb_grab_key_checked`](https://github.com/zealdocs/zeal/blob/master/src/3rdparty/qxtglobalshortcut/qxtglobalshortcut_x11.cpp#L142). The reason why my hotkey has no effect, is that the key reported by the nativeEventFilter is the one in `keycodes.data()[1]`. keycodes.data()[0] is adiaeresis (german Ä). Now I know that after registering <kbd>Alt</kbd>+<kbd>Y</kbd>, I can open zeal by pressing <kbd>Alt</kbd>+<kbd>Ä</kbd>.
Well I printed my keycode mapping like this (xmodmap -pke does it as well)
``` cpp
for (int cc =0 ; cc<256; ++cc){
qDebug() << cc << XKeysymToString(xcb_key_symbols_get_keysym(xcbKeySymbols,cc,0))
<< XKeysymToString(xcb_key_symbols_get_keysym(xcbKeySymbols,cc,1))
<< XKeysymToString(xcb_key_symbols_get_keysym(xcbKeySymbols,cc,2))
<< XKeysymToString(xcb_key_symbols_get_keysym(xcbKeySymbols,cc,3))
<< XKeysymToString(xcb_key_symbols_get_keysym(xcbKeySymbols,cc,4))
<< XKeysymToString(xcb_key_symbols_get_keysym(xcbKeySymbols,cc,6))
<< XKeysymToString(xcb_key_symbols_get_keysym(xcbKeySymbols,cc,7))
<< XKeysymToString(xcb_key_symbols_get_keysym(xcbKeySymbols,cc,8));
}
```
which looks like this (snippet)
```
48 adiaeresis Adiaeresis y Y dead_circumflex at Greek_upsilon period
49 dead_circumflex degree dead_circumflex dead_caron U2032 U21BB U02DE dead_abovedot
50 Shift_L Shift_L Caps_Lock
51 numbersign apostrophe ISO_Level3_Shift rightsinglequotemark
52 y Y udiaeresis Udiaeresis guillemotright numbersign Escape
```
And, yes, keysym Y (keycode 52 on my keyboard) is listed in the mapping of keycode 48 ( keysym Ä on my keyboard)... I stopped here working on this. Well this stuff is boring and annoying. Even xcb itelf states
> At the moment, XCB implements only a basic and incomplete sets of keyboard functions. Therefore, it greatly restricts the usages of XCB in "real-world" applications and duplicate the efforts as most applications ported to XCB so far (such as Awesome Window Manager, VLC and others) have to write their own implementation, which is often incomplete and buggy as it is rather tricky to implement properly and entirely.
I wish nobody to have to do this again, so I want to ask, if you are willing to make some kind of qxt-community organization (or soimething like that, doesnt have to be qxt). Qxt has been discontinued and there are several projects that are maintaining qxtglobalshortcut on their own, e.g. CopyQ, zeal, albert (mine, partially). If we'd unite our effort we could have more stability for less effort.
I think of a separated library for hotkey handling, not even necessarily using Qt.
|
defect
|
hotkeys do not work on certain keyboard mappings i recognized that several hotkeys do not work on my machine arch linux xorg server i even encountered a segfault the problematic line is when there is no keycode this will result in a segfault i debugged the code and realized that the keys reported by the nativeeventfilter are different from the ones that i wanted to be grabbed before via the reason why my hotkey has no effect is that the key reported by the nativeeventfilter is the one in keycodes data keycodes data is adiaeresis german ä now i know that after registering alt y i can open zeal by pressing alt ä well i printed my keycode mapping like this xmodmap pke does it as well cpp for int cc cc cc qdebug cc xkeysymtostring xcb key symbols get keysym xcbkeysymbols cc xkeysymtostring xcb key symbols get keysym xcbkeysymbols cc xkeysymtostring xcb key symbols get keysym xcbkeysymbols cc xkeysymtostring xcb key symbols get keysym xcbkeysymbols cc xkeysymtostring xcb key symbols get keysym xcbkeysymbols cc xkeysymtostring xcb key symbols get keysym xcbkeysymbols cc xkeysymtostring xcb key symbols get keysym xcbkeysymbols cc xkeysymtostring xcb key symbols get keysym xcbkeysymbols cc which looks like this snippet adiaeresis adiaeresis y y dead circumflex at greek upsilon period dead circumflex degree dead circumflex dead caron dead abovedot shift l shift l caps lock numbersign apostrophe iso shift rightsinglequotemark y y udiaeresis udiaeresis guillemotright numbersign escape and yes keysym y keycode on my keyboard is listed in the mapping of keycode keysym ä on my keyboard i stopped here working on this well this stuff is boring and annoying even xcb itelf states at the moment xcb implements only a basic and incomplete sets of keyboard functions therefore it greatly restricts the usages of xcb in real world applications and duplicate the efforts as most applications ported to xcb so far such as awesome window manager vlc and others have to write their own implementation which is often incomplete and buggy as it is rather tricky to implement properly and entirely i wish nobody to have to do this again so i want to ask if you are willing to make some kind of qxt community organization or soimething like that doesnt have to be qxt qxt has been discontinued and there are several projects that are maintaining qxtglobalshortcut on their own e g copyq zeal albert mine partially if we d unite our effort we could have more stability for less effort i think of a separated library for hotkey handling not even necessarily using qt
| 1
|
13,159
| 2,734,936,854
|
IssuesEvent
|
2015-04-17 23:51:26
|
cbeyls/slimbox
|
https://api.github.com/repos/cbeyls/slimbox
|
closed
|
Flash player are disappearing after opening and closing slimbox
|
auto-migrated Priority-Medium Type-Defect
|
```
What steps will reproduce the problem?
1. Set slimbox and flash player in one page
2. Open slimbox gallery.
3. After closing slimbox
It will set visibility to hidden to Flash player, so it will disappear but i
need flash player to be there as it is.
I am using 1.71 are you using? On unix operating system?
```
Original issue reported on code.google.com by `pradeep0...@gmail.com` on 8 Jul 2010 at 11:01
|
1.0
|
Flash player are disappearing after opening and closing slimbox - ```
What steps will reproduce the problem?
1. Set slimbox and flash player in one page
2. Open slimbox gallery.
3. After closing slimbox
It will set visibility to hidden to Flash player, so it will disappear but i
need flash player to be there as it is.
I am using 1.71 are you using? On unix operating system?
```
Original issue reported on code.google.com by `pradeep0...@gmail.com` on 8 Jul 2010 at 11:01
|
defect
|
flash player are disappearing after opening and closing slimbox what steps will reproduce the problem set slimbox and flash player in one page open slimbox gallery after closing slimbox it will set visibility to hidden to flash player so it will disappear but i need flash player to be there as it is i am using are you using on unix operating system original issue reported on code google com by gmail com on jul at
| 1
|
104,377
| 13,064,691,698
|
IssuesEvent
|
2020-07-30 18:30:40
|
ChrisNZL/Tallowmere2
|
https://api.github.com/repos/ChrisNZL/Tallowmere2
|
opened
|
Extra Mobs: Design considerations
|
♟ design consideration ⚠ priority 🍄 gameplay enhancement
|
v0.1.0 introduced a gameplay change:
- Extra enemies from curses and room modifiers no longer drop gold nor souls.
This change was made because:
- Enemies level-up based on room number, which guesses what the player’s level probably is.
- By having the player gain extra gold and souls from extra mobs via curses (and considering that’s the only curse type in the game as of v0.1.x), the player would snowball stronger much faster than the game expected.
Things to double-check:
- Does the game factor in extra mobs from curses?
- Do extra mobs count towards weapon and character unlocking?
Things to consider changing:
- Make soulless mobs change their appearance (Grey-looking? Smokey? Slightly different eyes? Black silhouettes?).
- Allow extra mobs from room modifiers still drop gold and souls, though perhaps with a lesser chance — or maybe still 100%, since room modifiers are just lucky rolls, not guaranteed changes like curses.
- Make “extra mobs spawn in pairs” curses not be 100%?
- By slaying a main / normal enemies, should its clone(s) be slain automatically? (Perhaps as a modifier?)
In any case, some of these issues will be not as dire once more curse types are implemented into the game, but some tweaking could still be good.
|
1.0
|
Extra Mobs: Design considerations - v0.1.0 introduced a gameplay change:
- Extra enemies from curses and room modifiers no longer drop gold nor souls.
This change was made because:
- Enemies level-up based on room number, which guesses what the player’s level probably is.
- By having the player gain extra gold and souls from extra mobs via curses (and considering that’s the only curse type in the game as of v0.1.x), the player would snowball stronger much faster than the game expected.
Things to double-check:
- Does the game factor in extra mobs from curses?
- Do extra mobs count towards weapon and character unlocking?
Things to consider changing:
- Make soulless mobs change their appearance (Grey-looking? Smokey? Slightly different eyes? Black silhouettes?).
- Allow extra mobs from room modifiers still drop gold and souls, though perhaps with a lesser chance — or maybe still 100%, since room modifiers are just lucky rolls, not guaranteed changes like curses.
- Make “extra mobs spawn in pairs” curses not be 100%?
- By slaying a main / normal enemies, should its clone(s) be slain automatically? (Perhaps as a modifier?)
In any case, some of these issues will be not as dire once more curse types are implemented into the game, but some tweaking could still be good.
|
non_defect
|
extra mobs design considerations introduced a gameplay change extra enemies from curses and room modifiers no longer drop gold nor souls this change was made because enemies level up based on room number which guesses what the player’s level probably is by having the player gain extra gold and souls from extra mobs via curses and considering that’s the only curse type in the game as of x the player would snowball stronger much faster than the game expected things to double check does the game factor in extra mobs from curses do extra mobs count towards weapon and character unlocking things to consider changing make soulless mobs change their appearance grey looking smokey slightly different eyes black silhouettes allow extra mobs from room modifiers still drop gold and souls though perhaps with a lesser chance — or maybe still since room modifiers are just lucky rolls not guaranteed changes like curses make “extra mobs spawn in pairs” curses not be by slaying a main normal enemies should its clone s be slain automatically perhaps as a modifier in any case some of these issues will be not as dire once more curse types are implemented into the game but some tweaking could still be good
| 0
|
673,768
| 23,030,252,697
|
IssuesEvent
|
2022-07-22 13:17:58
|
webcompat/web-bugs
|
https://api.github.com/repos/webcompat/web-bugs
|
closed
|
coinmarketcap.com - site is not usable
|
priority-important browser-focus-geckoview engine-gecko type-private-browsing
|
<!-- @browser: Firefox Mobile 102.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 12; Mobile; rv:102.0) Gecko/102.0 Firefox/102.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/107796 -->
<!-- @extra_labels: browser-focus-geckoview -->
**URL**: https://coinmarketcap.com/currencies/polygon/
**Browser / Version**: Firefox Mobile 102.0
**Operating System**: Android 12
**Tested Another Browser**: Yes Other
**Problem type**: Site is not usable
**Description**: Page not loading correctly
**Steps to Reproduce**:
Page loads normally and then it turns completely blank
<details>
<summary>View the screenshot</summary>
<img alt="Screenshot" src="https://webcompat.com/uploads/2022/7/b271e061-2bf1-48e0-985f-af7ad85e3a0c.jpeg">
</details>
<details>
<summary>Browser Configuration</summary>
<ul>
<li>gfx.webrender.all: false</li><li>gfx.webrender.blob-images: true</li><li>gfx.webrender.enabled: false</li><li>image.mem.shared: true</li><li>buildID: 20220705093820</li><li>channel: release</li><li>hasTouchScreen: true</li><li>mixed active content blocked: false</li><li>mixed passive content blocked: false</li><li>tracking content blocked: false</li>
</ul>
</details>
[View console log messages](https://webcompat.com/console_logs/2022/7/435e626b-00ea-4b22-a4dc-78a443722506)
_From [webcompat.com](https://webcompat.com/) with ❤️_
|
1.0
|
coinmarketcap.com - site is not usable - <!-- @browser: Firefox Mobile 102.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 12; Mobile; rv:102.0) Gecko/102.0 Firefox/102.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/107796 -->
<!-- @extra_labels: browser-focus-geckoview -->
**URL**: https://coinmarketcap.com/currencies/polygon/
**Browser / Version**: Firefox Mobile 102.0
**Operating System**: Android 12
**Tested Another Browser**: Yes Other
**Problem type**: Site is not usable
**Description**: Page not loading correctly
**Steps to Reproduce**:
Page loads normally and then it turns completely blank
<details>
<summary>View the screenshot</summary>
<img alt="Screenshot" src="https://webcompat.com/uploads/2022/7/b271e061-2bf1-48e0-985f-af7ad85e3a0c.jpeg">
</details>
<details>
<summary>Browser Configuration</summary>
<ul>
<li>gfx.webrender.all: false</li><li>gfx.webrender.blob-images: true</li><li>gfx.webrender.enabled: false</li><li>image.mem.shared: true</li><li>buildID: 20220705093820</li><li>channel: release</li><li>hasTouchScreen: true</li><li>mixed active content blocked: false</li><li>mixed passive content blocked: false</li><li>tracking content blocked: false</li>
</ul>
</details>
[View console log messages](https://webcompat.com/console_logs/2022/7/435e626b-00ea-4b22-a4dc-78a443722506)
_From [webcompat.com](https://webcompat.com/) with ❤️_
|
non_defect
|
coinmarketcap com site is not usable url browser version firefox mobile operating system android tested another browser yes other problem type site is not usable description page not loading correctly steps to reproduce page loads normally and then it turns completely blank view the screenshot img alt screenshot src browser configuration gfx webrender all false gfx webrender blob images true gfx webrender enabled false image mem shared true buildid channel release hastouchscreen true mixed active content blocked false mixed passive content blocked false tracking content blocked false from with ❤️
| 0
|
293,911
| 25,332,992,194
|
IssuesEvent
|
2022-11-18 14:40:34
|
NationalSecurityAgency/skills-service
|
https://api.github.com/repos/NationalSecurityAgency/skills-service
|
closed
|
Ability to split self-approval workload between multiple Approvers or Admins
|
enhancement test
|
Create a flexible way for project admins to configure a split of the self-approval workload:
* users can be assigned one-by-one to a specific approver/admin
* users can be assigned by user's tag (server config optionally enabled feature)
* ability to designate a catch-all approver - designate an approver for any users that are not already assigned to an approved
* as a fallback, if such person is not designated then approve requests will be forwarded to the admins
Depends on #648
|
1.0
|
Ability to split self-approval workload between multiple Approvers or Admins - Create a flexible way for project admins to configure a split of the self-approval workload:
* users can be assigned one-by-one to a specific approver/admin
* users can be assigned by user's tag (server config optionally enabled feature)
* ability to designate a catch-all approver - designate an approver for any users that are not already assigned to an approved
* as a fallback, if such person is not designated then approve requests will be forwarded to the admins
Depends on #648
|
non_defect
|
ability to split self approval workload between multiple approvers or admins create a flexible way for project admins to configure a split of the self approval workload users can be assigned one by one to a specific approver admin users can be assigned by user s tag server config optionally enabled feature ability to designate a catch all approver designate an approver for any users that are not already assigned to an approved as a fallback if such person is not designated then approve requests will be forwarded to the admins depends on
| 0
|
147,322
| 11,781,833,777
|
IssuesEvent
|
2020-03-16 23:42:59
|
rancher/rancher
|
https://api.github.com/repos/rancher/rancher
|
closed
|
Show CIS scan error message in UI
|
[zube]: To Test area/scan-tool team/ui
|
https://github.com/rancher/rancher/issues/24626#issuecomment-583784157
Now that the error message is returned from backend, we need to show this in UI when a cluster scan has errored out.
|
1.0
|
Show CIS scan error message in UI - https://github.com/rancher/rancher/issues/24626#issuecomment-583784157
Now that the error message is returned from backend, we need to show this in UI when a cluster scan has errored out.
|
non_defect
|
show cis scan error message in ui now that the error message is returned from backend we need to show this in ui when a cluster scan has errored out
| 0
|
156,908
| 12,340,890,538
|
IssuesEvent
|
2020-05-14 20:47:45
|
cockroachdb/cockroach
|
https://api.github.com/repos/cockroachdb/cockroach
|
closed
|
roachtest: django failed
|
C-test-failure O-roachtest O-robot branch-provisional_202005112258_v19.2.7 release-blocker
|
[(roachtest).django failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=1937028&tab=buildLog) on [provisional_202005112258_v19.2.7@a06674c55934425114e99ae2f9751b948d5c1d93](https://github.com/cockroachdb/cockroach/commits/a06674c55934425114e99ae2f9751b948d5c1d93):
```
The test failed on branch=provisional_202005112258_v19.2.7, cloud=gce:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/django/run_1
cluster.go:1481,context.go:135,cluster.go:1470,test_runner.go:825: dead node detection: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod monitor teamcity-1937028-1589298914-35-n1cpu16 --oneshot --ignore-empty-nodes: exit status 1 1: dead
Error: UNCLASSIFIED_PROBLEM: 1: dead
(1) UNCLASSIFIED_PROBLEM
Wraps: (2) attached stack trace
| main.glob..func13
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1129
| main.wrap.func1
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:272
| github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra.(*Command).execute
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra/command.go:766
| github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra.(*Command).ExecuteC
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra/command.go:852
| github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra.(*Command).Execute
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra/command.go:800
| main.main
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1799
| runtime.main
| /usr/local/go/src/runtime/proc.go:203
| runtime.goexit
| /usr/local/go/src/runtime/asm_amd64.s:1357
Wraps: (3) 1: dead
Error types: (1) errors.Unclassified (2) *withstack.withStack (3) *errors.errorString
```
<details><summary>More</summary><p>
Artifacts: [/django](https://teamcity.cockroachdb.com/viewLog.html?buildId=1937028&tab=artifacts#/django)
Related:
- #48653 roachtest: django failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-provisional_202005041959_v19.2.7](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-provisional_202005041959_v19.2.7) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #47931 roachtest: django failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-provisional_202004210018_v20.1.0](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-provisional_202004210018_v20.1.0) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #47658 roachtest: django failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-provisional_202004171855_v20.1.0-rc.2](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-provisional_202004171855_v20.1.0-rc.2) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #47282 roachtest: django failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-provisional_202004061746_v19.2.6](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-provisional_202004061746_v19.2.6) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #46800 roachtest: django failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-release-20.1](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-release-20.1) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #44477 roachtest: django failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-release-19.2](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-release-19.2)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Adjango.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
|
2.0
|
roachtest: django failed - [(roachtest).django failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=1937028&tab=buildLog) on [provisional_202005112258_v19.2.7@a06674c55934425114e99ae2f9751b948d5c1d93](https://github.com/cockroachdb/cockroach/commits/a06674c55934425114e99ae2f9751b948d5c1d93):
```
The test failed on branch=provisional_202005112258_v19.2.7, cloud=gce:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/django/run_1
cluster.go:1481,context.go:135,cluster.go:1470,test_runner.go:825: dead node detection: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod monitor teamcity-1937028-1589298914-35-n1cpu16 --oneshot --ignore-empty-nodes: exit status 1 1: dead
Error: UNCLASSIFIED_PROBLEM: 1: dead
(1) UNCLASSIFIED_PROBLEM
Wraps: (2) attached stack trace
| main.glob..func13
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1129
| main.wrap.func1
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:272
| github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra.(*Command).execute
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra/command.go:766
| github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra.(*Command).ExecuteC
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra/command.go:852
| github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra.(*Command).Execute
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra/command.go:800
| main.main
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1799
| runtime.main
| /usr/local/go/src/runtime/proc.go:203
| runtime.goexit
| /usr/local/go/src/runtime/asm_amd64.s:1357
Wraps: (3) 1: dead
Error types: (1) errors.Unclassified (2) *withstack.withStack (3) *errors.errorString
```
<details><summary>More</summary><p>
Artifacts: [/django](https://teamcity.cockroachdb.com/viewLog.html?buildId=1937028&tab=artifacts#/django)
Related:
- #48653 roachtest: django failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-provisional_202005041959_v19.2.7](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-provisional_202005041959_v19.2.7) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #47931 roachtest: django failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-provisional_202004210018_v20.1.0](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-provisional_202004210018_v20.1.0) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #47658 roachtest: django failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-provisional_202004171855_v20.1.0-rc.2](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-provisional_202004171855_v20.1.0-rc.2) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #47282 roachtest: django failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-provisional_202004061746_v19.2.6](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-provisional_202004061746_v19.2.6) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #46800 roachtest: django failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-release-20.1](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-release-20.1) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #44477 roachtest: django failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-release-19.2](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-release-19.2)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Adjango.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
|
non_defect
|
roachtest django failed on the test failed on branch provisional cloud gce test artifacts and logs in home agent work go src github com cockroachdb cockroach artifacts django run cluster go context go cluster go test runner go dead node detection home agent work go src github com cockroachdb cockroach bin roachprod monitor teamcity oneshot ignore empty nodes exit status dead error unclassified problem dead unclassified problem wraps attached stack trace main glob home agent work go src github com cockroachdb cockroach pkg cmd roachprod main go main wrap home agent work go src github com cockroachdb cockroach pkg cmd roachprod main go github com cockroachdb cockroach vendor github com cobra command execute home agent work go src github com cockroachdb cockroach vendor github com cobra command go github com cockroachdb cockroach vendor github com cobra command executec home agent work go src github com cockroachdb cockroach vendor github com cobra command go github com cockroachdb cockroach vendor github com cobra command execute home agent work go src github com cockroachdb cockroach vendor github com cobra command go main main home agent work go src github com cockroachdb cockroach pkg cmd roachprod main go runtime main usr local go src runtime proc go runtime goexit usr local go src runtime asm s wraps dead error types errors unclassified withstack withstack errors errorstring more artifacts related roachtest django failed roachtest django failed roachtest django failed roachtest django failed roachtest django failed roachtest django failed powered by
| 0
|
109,947
| 23,847,273,094
|
IssuesEvent
|
2022-09-06 14:53:58
|
gitpod-io/gitpod
|
https://api.github.com/repos/gitpod-io/gitpod
|
closed
|
[code-desktop] Align on a way to ensure Gitpod API compatibility between IDE clients and SH installations.
|
self-hosted component: server team: IDE editor: code (desktop)
|
- We decided to change how ouath2 endpoint works. It should ignore unknown scopes, verify and return only subset of known scopes. Clients should use returned scopes as source of truth to check whether features are present. It is for instance how GitHub auth works.
- We will still need to adhere to `api/version` for 2 SH releases which has changes to ouath2 endpoint. After this check can be removed.
Internal RFC [[1](https://www.notion.so/gitpod/Gitpod-Server-API-compatibility-check-ee00fcfe60a84c1e8e018ab6c06c1f5d)]
|
1.0
|
[code-desktop] Align on a way to ensure Gitpod API compatibility between IDE clients and SH installations. - - We decided to change how ouath2 endpoint works. It should ignore unknown scopes, verify and return only subset of known scopes. Clients should use returned scopes as source of truth to check whether features are present. It is for instance how GitHub auth works.
- We will still need to adhere to `api/version` for 2 SH releases which has changes to ouath2 endpoint. After this check can be removed.
Internal RFC [[1](https://www.notion.so/gitpod/Gitpod-Server-API-compatibility-check-ee00fcfe60a84c1e8e018ab6c06c1f5d)]
|
non_defect
|
align on a way to ensure gitpod api compatibility between ide clients and sh installations we decided to change how endpoint works it should ignore unknown scopes verify and return only subset of known scopes clients should use returned scopes as source of truth to check whether features are present it is for instance how github auth works we will still need to adhere to api version for sh releases which has changes to endpoint after this check can be removed internal rfc
| 0
|
71,770
| 23,794,350,302
|
IssuesEvent
|
2022-09-02 17:46:13
|
department-of-veterans-affairs/va.gov-team
|
https://api.github.com/repos/department-of-veterans-affairs/va.gov-team
|
opened
|
508-defect-4 [DESCRIPTIVE TEXT] Profile - Notification Settings: No announcement of the type of telephone number (mobile) being read aloud
|
508/Accessibility 508-defect-4 508-issue-screenreader
|
### Point of contact
@TiffanyPender
### Severity level
4, Minor. Consider fixing or exploring in 2-4 sprints post-launch.
### Details
As a screen reader user, it is important that content is properly labeled so that I can understand the type of information that is being presented.
Within Profile Notification Settings, near the top of the content, the Veteran’s mobile number is listed, followed by a link to update their mobile phone number. The text content listed beforehand does not truly indicate what type of phone number is being read aloud by screen readers. Users may be able to guess that this is their mobile number, but the lack of specific callout text may create confusion.
### Reproduction steps
1. In staging, login to a LOA3 user's account.
2. Navigate to [Profile](https://staging.va.gov/profile) - Notification Settings
3. With a screen reader, after "We'll use the contact information from your profile to send you the notifications you choose," verify that there is no text read aloud that indicates a mobile number is about to be read.
### Proposed solution or next steps
Add in additional text before the listed mobile number to indicate that this is the Veteran’s mobile number on file. This information would be beneficial to all users, not just screen reader users.
### References, articles, or WCAG support
[1.3.1 Info and Relationships](https://www.w3.org/WAI/WCAG21/quickref/#info-and-relationships)
[4.1.2 Name, Role, Value](https://www.w3.org/WAI/WCAG21/quickref/#name-role-value)
### Type of issue
- [ ] Screenreader
- [ ] Keyboard
- [ ] Focus
- [ ] Headings
- [ ] Color
- [ ] Zoom
- [ ] Semantics
- [ ] Axe-core
- [X] Something else
|
1.0
|
508-defect-4 [DESCRIPTIVE TEXT] Profile - Notification Settings: No announcement of the type of telephone number (mobile) being read aloud - ### Point of contact
@TiffanyPender
### Severity level
4, Minor. Consider fixing or exploring in 2-4 sprints post-launch.
### Details
As a screen reader user, it is important that content is properly labeled so that I can understand the type of information that is being presented.
Within Profile Notification Settings, near the top of the content, the Veteran’s mobile number is listed, followed by a link to update their mobile phone number. The text content listed beforehand does not truly indicate what type of phone number is being read aloud by screen readers. Users may be able to guess that this is their mobile number, but the lack of specific callout text may create confusion.
### Reproduction steps
1. In staging, login to a LOA3 user's account.
2. Navigate to [Profile](https://staging.va.gov/profile) - Notification Settings
3. With a screen reader, after "We'll use the contact information from your profile to send you the notifications you choose," verify that there is no text read aloud that indicates a mobile number is about to be read.
### Proposed solution or next steps
Add in additional text before the listed mobile number to indicate that this is the Veteran’s mobile number on file. This information would be beneficial to all users, not just screen reader users.
### References, articles, or WCAG support
[1.3.1 Info and Relationships](https://www.w3.org/WAI/WCAG21/quickref/#info-and-relationships)
[4.1.2 Name, Role, Value](https://www.w3.org/WAI/WCAG21/quickref/#name-role-value)
### Type of issue
- [ ] Screenreader
- [ ] Keyboard
- [ ] Focus
- [ ] Headings
- [ ] Color
- [ ] Zoom
- [ ] Semantics
- [ ] Axe-core
- [X] Something else
|
defect
|
defect profile notification settings no announcement of the type of telephone number mobile being read aloud point of contact tiffanypender severity level minor consider fixing or exploring in sprints post launch details as a screen reader user it is important that content is properly labeled so that i can understand the type of information that is being presented within profile notification settings near the top of the content the veteran’s mobile number is listed followed by a link to update their mobile phone number the text content listed beforehand does not truly indicate what type of phone number is being read aloud by screen readers users may be able to guess that this is their mobile number but the lack of specific callout text may create confusion reproduction steps in staging login to a user s account navigate to notification settings with a screen reader after we ll use the contact information from your profile to send you the notifications you choose verify that there is no text read aloud that indicates a mobile number is about to be read proposed solution or next steps add in additional text before the listed mobile number to indicate that this is the veteran’s mobile number on file this information would be beneficial to all users not just screen reader users references articles or wcag support type of issue screenreader keyboard focus headings color zoom semantics axe core something else
| 1
|
20,920
| 3,436,323,934
|
IssuesEvent
|
2015-12-12 08:59:52
|
Xebeth/lootbox
|
https://api.github.com/repos/Xebeth/lootbox
|
closed
|
most bugs
|
auto-migrated Priority-Medium Type-Defect
|
```
What steps will reproduce the problem?
1. Open lootbox
2. check new items invenctory
3. I see most errors or empy field or duplicate items whit wrong description.
For example Windbuffet belt or Fortitude Torque
What is the expected output? What do you see instead?
The name and description of the items
What version of the product are you using? On what operating system?
Last ver of lootbox on Windows 7 64bit updated.
Please provide any additional information below.
```
Original issue reported on code.google.com by `RonnieVe...@gmail.com` on 4 Jan 2014 at 6:28
Attachments:
* [errors.png](https://storage.googleapis.com/google-code-attachments/lootbox/issue-3/comment-0/errors.png)
|
1.0
|
most bugs - ```
What steps will reproduce the problem?
1. Open lootbox
2. check new items invenctory
3. I see most errors or empy field or duplicate items whit wrong description.
For example Windbuffet belt or Fortitude Torque
What is the expected output? What do you see instead?
The name and description of the items
What version of the product are you using? On what operating system?
Last ver of lootbox on Windows 7 64bit updated.
Please provide any additional information below.
```
Original issue reported on code.google.com by `RonnieVe...@gmail.com` on 4 Jan 2014 at 6:28
Attachments:
* [errors.png](https://storage.googleapis.com/google-code-attachments/lootbox/issue-3/comment-0/errors.png)
|
defect
|
most bugs what steps will reproduce the problem open lootbox check new items invenctory i see most errors or empy field or duplicate items whit wrong description for example windbuffet belt or fortitude torque what is the expected output what do you see instead the name and description of the items what version of the product are you using on what operating system last ver of lootbox on windows updated please provide any additional information below original issue reported on code google com by ronnieve gmail com on jan at attachments
| 1
|
60,724
| 25,235,207,071
|
IssuesEvent
|
2022-11-14 23:55:51
|
open-telemetry/opentelemetry-collector
|
https://api.github.com/repos/open-telemetry/opentelemetry-collector
|
closed
|
Question about how to configure zap logger
|
enhancement priority:p3 release:after-ga area:service
|
I built a custom collector using [this guide](https://medium.com/opentelemetry/building-your-own-opentelemetry-collector-distribution-42337e994b63) with collector v0.16.0.
Everything works great, except that I need to configure the logger to output json format with MessageKey equals "message" (instead of the default "msg").
I want to be able to set this configuration when calling service.New:
`conf.EncoderConfig.MessageKey = "message"`
My current code looks like this:
```go
app, err := service.New(service.Parameters{ApplicationStartInfo: info, Factories: factories, LoggingOptions: loggingOptions})
```
but was not able to understand how to set EncoderConfig with LoggingOptions.
Is it possible? any help will be appreciated as I'm new to GO. thanks
|
1.0
|
Question about how to configure zap logger - I built a custom collector using [this guide](https://medium.com/opentelemetry/building-your-own-opentelemetry-collector-distribution-42337e994b63) with collector v0.16.0.
Everything works great, except that I need to configure the logger to output json format with MessageKey equals "message" (instead of the default "msg").
I want to be able to set this configuration when calling service.New:
`conf.EncoderConfig.MessageKey = "message"`
My current code looks like this:
```go
app, err := service.New(service.Parameters{ApplicationStartInfo: info, Factories: factories, LoggingOptions: loggingOptions})
```
but was not able to understand how to set EncoderConfig with LoggingOptions.
Is it possible? any help will be appreciated as I'm new to GO. thanks
|
non_defect
|
question about how to configure zap logger i built a custom collector using with collector everything works great except that i need to configure the logger to output json format with messagekey equals message instead of the default msg i want to be able to set this configuration when calling service new conf encoderconfig messagekey message my current code looks like this go app err service new service parameters applicationstartinfo info factories factories loggingoptions loggingoptions but was not able to understand how to set encoderconfig with loggingoptions is it possible any help will be appreciated as i m new to go thanks
| 0
|
33,487
| 7,132,023,479
|
IssuesEvent
|
2018-01-22 13:16:06
|
line/armeria
|
https://api.github.com/repos/line/armeria
|
opened
|
Disable path mapping cache for prefix mapping
|
defect new-feature
|
We currently cache a path mapping result as long as the response status is successful and the mapping does not have any path parameters: https://github.com/line/armeria/blob/8e6cbc36a92de7ae3e03a41531e7ab486cd0121a/core/src/main/java/com/linecorp/armeria/server/HttpServerHandler.java#L334
This does not work well with prefix mapping which can map to infinit number of paths, because the mapping result will always have zero path parameters.
To address this issue, we could:
1. Disable caching for prefix mapping by default
2. Provide a way to enable path mapping caching for some special cases, e.g. `HttpFileService` would use prefix mapping but still could use cache because it will return successful response status for a limited number of paths.
- Annotation? e.g. `@EnablePathMappingCache`
- Interface?
```java
public interface SomeInterfaceThatServiceWillImplement {
boolean canCache(PathMapping, PathAndQuery);
}
```
Thoughts?
/cc @hyangtack @huydx @anuraaga
|
1.0
|
Disable path mapping cache for prefix mapping - We currently cache a path mapping result as long as the response status is successful and the mapping does not have any path parameters: https://github.com/line/armeria/blob/8e6cbc36a92de7ae3e03a41531e7ab486cd0121a/core/src/main/java/com/linecorp/armeria/server/HttpServerHandler.java#L334
This does not work well with prefix mapping which can map to infinit number of paths, because the mapping result will always have zero path parameters.
To address this issue, we could:
1. Disable caching for prefix mapping by default
2. Provide a way to enable path mapping caching for some special cases, e.g. `HttpFileService` would use prefix mapping but still could use cache because it will return successful response status for a limited number of paths.
- Annotation? e.g. `@EnablePathMappingCache`
- Interface?
```java
public interface SomeInterfaceThatServiceWillImplement {
boolean canCache(PathMapping, PathAndQuery);
}
```
Thoughts?
/cc @hyangtack @huydx @anuraaga
|
defect
|
disable path mapping cache for prefix mapping we currently cache a path mapping result as long as the response status is successful and the mapping does not have any path parameters this does not work well with prefix mapping which can map to infinit number of paths because the mapping result will always have zero path parameters to address this issue we could disable caching for prefix mapping by default provide a way to enable path mapping caching for some special cases e g httpfileservice would use prefix mapping but still could use cache because it will return successful response status for a limited number of paths annotation e g enablepathmappingcache interface java public interface someinterfacethatservicewillimplement boolean cancache pathmapping pathandquery thoughts cc hyangtack huydx anuraaga
| 1
|
82,145
| 10,226,205,143
|
IssuesEvent
|
2019-08-16 17:09:39
|
flutter/flutter
|
https://api.github.com/repos/flutter/flutter
|
closed
|
ListTile.divideTiles creates dividers that don't meet Material spec
|
customer: mulligan (g3) f: material design framework
|
Divider's are supposed to be 1dp according to the material spec. However, `ListTile.divideTiles` builds hairline (1px) dividers.

https://material.io/design/components/dividers.html#implementation
|
1.0
|
ListTile.divideTiles creates dividers that don't meet Material spec - Divider's are supposed to be 1dp according to the material spec. However, `ListTile.divideTiles` builds hairline (1px) dividers.

https://material.io/design/components/dividers.html#implementation
|
non_defect
|
listtile dividetiles creates dividers that don t meet material spec divider s are supposed to be according to the material spec however listtile dividetiles builds hairline dividers
| 0
|
618,001
| 19,412,040,674
|
IssuesEvent
|
2021-12-20 10:39:53
|
bobbingwide/oik-plugins
|
https://api.github.com/repos/bobbingwide/oik-plugins
|
closed
|
Support the sb-field-block
|
enhancement Gutenberg Priority B Severity 2
|
The https://github.com/bobbingwide/sb-field-block plugin is new block to display and enable updating of post meta data.
It will replace the Fields meta box and the [bw_field] / [bw_fields] shortcodes.
In order to support access to post meta fields a post type needs to be registered with post type supports `custom-fields`
and each field has to be defined as `show-in-rest`.
Themes that use oik-plugins will eventually switch to using the block rather than the shortcodes.
The first thing to do is to enable this capability.
See https://github.com/bobbingwide/sb-field-block/issues/2
|
1.0
|
Support the sb-field-block - The https://github.com/bobbingwide/sb-field-block plugin is new block to display and enable updating of post meta data.
It will replace the Fields meta box and the [bw_field] / [bw_fields] shortcodes.
In order to support access to post meta fields a post type needs to be registered with post type supports `custom-fields`
and each field has to be defined as `show-in-rest`.
Themes that use oik-plugins will eventually switch to using the block rather than the shortcodes.
The first thing to do is to enable this capability.
See https://github.com/bobbingwide/sb-field-block/issues/2
|
non_defect
|
support the sb field block the plugin is new block to display and enable updating of post meta data it will replace the fields meta box and the shortcodes in order to support access to post meta fields a post type needs to be registered with post type supports custom fields and each field has to be defined as show in rest themes that use oik plugins will eventually switch to using the block rather than the shortcodes the first thing to do is to enable this capability see
| 0
|
71,119
| 23,455,285,306
|
IssuesEvent
|
2022-08-16 08:20:05
|
vector-im/element-ios
|
https://api.github.com/repos/vector-im/element-ios
|
opened
|
Can't ineract with message because of reactions feature
|
T-Defect
|
### Steps to reproduce
Both problems are shown in the video below.
### First problem
1. Send a .m4a Audio File from Desktop Element
2. Try to play the Audio in the iOS App
### Second problem
iOS does create a Calendar Link, if the text has any time mentioned. These links are not clickable because of the reaction feature.
1. Send a text with for example a date (20.09.2022)
2. try to click the link iOS creates
https://user-images.githubusercontent.com/51084761/184832295-094c982a-f992-4d15-bf58-6bd04a673d4d.mov
### Outcome
### First problem
#### What did you expect?
iOS App should play the audio.
#### What happened instead?
Reactions feature does open.
### Second problem
#### What did you expect?
#### What happened instead?
### Your phone model
iPhone XR
### Operating system version
15.6
### Application version
1.8.27
### Homeserver
_No response_
### Will you send logs?
No
|
1.0
|
Can't ineract with message because of reactions feature - ### Steps to reproduce
Both problems are shown in the video below.
### First problem
1. Send a .m4a Audio File from Desktop Element
2. Try to play the Audio in the iOS App
### Second problem
iOS does create a Calendar Link, if the text has any time mentioned. These links are not clickable because of the reaction feature.
1. Send a text with for example a date (20.09.2022)
2. try to click the link iOS creates
https://user-images.githubusercontent.com/51084761/184832295-094c982a-f992-4d15-bf58-6bd04a673d4d.mov
### Outcome
### First problem
#### What did you expect?
iOS App should play the audio.
#### What happened instead?
Reactions feature does open.
### Second problem
#### What did you expect?
#### What happened instead?
### Your phone model
iPhone XR
### Operating system version
15.6
### Application version
1.8.27
### Homeserver
_No response_
### Will you send logs?
No
|
defect
|
can t ineract with message because of reactions feature steps to reproduce both problems are shown in the video below first problem send a audio file from desktop element try to play the audio in the ios app second problem ios does create a calendar link if the text has any time mentioned these links are not clickable because of the reaction feature send a text with for example a date try to click the link ios creates outcome first problem what did you expect ios app should play the audio what happened instead reactions feature does open second problem what did you expect what happened instead your phone model iphone xr operating system version application version homeserver no response will you send logs no
| 1
|
35,852
| 14,889,816,533
|
IssuesEvent
|
2021-01-20 22:00:34
|
Azure/azure-cli
|
https://api.github.com/repos/Azure/azure-cli
|
closed
|
AKS Template deployment fails when providing a keyvault reference to the "servicePrincipalProfile" attribute.
|
AKS ARM - Templates Service Attention
|
### **This is autogenerated. Please review and update as needed.**
## Describe the bug
When deploying an arm template for AKS, the "servicePrincipalProfile" cannot retrieve secrets from keyvault based on dynamic values (as described here : [Keyvault dynamic ids](https://docs.microsoft.com/en-us/azure/azure-resource-manager/templates/key-vault-parameter?tabs=azure-cli)).
When providing the following
```
"servicePrincipalProfile": {
"clientId": "[parameters('serviceSpnId')]",
"Secret": {
"reference": {
"keyVault": {
"id": "[resourceId(parameters('subscriptionId'), parameters('resourceGroup'), 'Microsoft.KeyVault/vaults', parameters('keyVaultName'))]"
},
"secretName": "[parameters('serviceSpnId')]"
}
}
}
```
to the resource/properties/servicePrincipalProfile of element of the template, the deployment failed with :
```
Deployment failed. Correlation ID: 9beefc6e-7fb3-4004-b77a-671e133c51cb. {
"code": "UnmarshalError",
"message": "UnmarshalEntity encountered error: json: cannot unmarshal object into Go struct field ServicePrincipalProfile.secret of type string."
}
```
**Command Name**
`az group deployment create`
**Errors:**
```
Deployment failed. Correlation ID: 9beefc6e-7fb3-4004-b77a-671e133c51cb. {
"code": "UnmarshalError",
"message": "UnmarshalEntity encountered error: json: cannot unmarshal object into Go struct field ServicePrincipalProfile.secret of type string."
}
```
## To Reproduce:
Steps to reproduce the behavior. Note that argument values have been redacted, as they may contain sensitive information.
- Create a template to deploy aks and set the servicePrincipalProfile to a keyvault reference in the teamplate.json
- `az group deployment create --resource-group {} --template-file {} --parameter {} --debug`
## Expected Behavior
I would expect the deployment to retrieve the secret based on the dynamic id.
## Environment Summary
```
Windows-10-10.0.18362-SP0
Python 3.6.6
Shell: cmd.exe
azure-cli 2.0.79 *
Extensions:
azure-devops 0.17.0
```
## Additional Context
<!--Please don't remove this:-->
<!--auto-generated-->
|
1.0
|
AKS Template deployment fails when providing a keyvault reference to the "servicePrincipalProfile" attribute. - ### **This is autogenerated. Please review and update as needed.**
## Describe the bug
When deploying an arm template for AKS, the "servicePrincipalProfile" cannot retrieve secrets from keyvault based on dynamic values (as described here : [Keyvault dynamic ids](https://docs.microsoft.com/en-us/azure/azure-resource-manager/templates/key-vault-parameter?tabs=azure-cli)).
When providing the following
```
"servicePrincipalProfile": {
"clientId": "[parameters('serviceSpnId')]",
"Secret": {
"reference": {
"keyVault": {
"id": "[resourceId(parameters('subscriptionId'), parameters('resourceGroup'), 'Microsoft.KeyVault/vaults', parameters('keyVaultName'))]"
},
"secretName": "[parameters('serviceSpnId')]"
}
}
}
```
to the resource/properties/servicePrincipalProfile of element of the template, the deployment failed with :
```
Deployment failed. Correlation ID: 9beefc6e-7fb3-4004-b77a-671e133c51cb. {
"code": "UnmarshalError",
"message": "UnmarshalEntity encountered error: json: cannot unmarshal object into Go struct field ServicePrincipalProfile.secret of type string."
}
```
**Command Name**
`az group deployment create`
**Errors:**
```
Deployment failed. Correlation ID: 9beefc6e-7fb3-4004-b77a-671e133c51cb. {
"code": "UnmarshalError",
"message": "UnmarshalEntity encountered error: json: cannot unmarshal object into Go struct field ServicePrincipalProfile.secret of type string."
}
```
## To Reproduce:
Steps to reproduce the behavior. Note that argument values have been redacted, as they may contain sensitive information.
- Create a template to deploy aks and set the servicePrincipalProfile to a keyvault reference in the teamplate.json
- `az group deployment create --resource-group {} --template-file {} --parameter {} --debug`
## Expected Behavior
I would expect the deployment to retrieve the secret based on the dynamic id.
## Environment Summary
```
Windows-10-10.0.18362-SP0
Python 3.6.6
Shell: cmd.exe
azure-cli 2.0.79 *
Extensions:
azure-devops 0.17.0
```
## Additional Context
<!--Please don't remove this:-->
<!--auto-generated-->
|
non_defect
|
aks template deployment fails when providing a keyvault reference to the serviceprincipalprofile attribute this is autogenerated please review and update as needed describe the bug when deploying an arm template for aks the serviceprincipalprofile cannot retrieve secrets from keyvault based on dynamic values as described here when providing the following serviceprincipalprofile clientid secret reference keyvault id secretname to the resource properties serviceprincipalprofile of element of the template the deployment failed with deployment failed correlation id code unmarshalerror message unmarshalentity encountered error json cannot unmarshal object into go struct field serviceprincipalprofile secret of type string command name az group deployment create errors deployment failed correlation id code unmarshalerror message unmarshalentity encountered error json cannot unmarshal object into go struct field serviceprincipalprofile secret of type string to reproduce steps to reproduce the behavior note that argument values have been redacted as they may contain sensitive information create a template to deploy aks and set the serviceprincipalprofile to a keyvault reference in the teamplate json az group deployment create resource group template file parameter debug expected behavior i would expect the deployment to retrieve the secret based on the dynamic id environment summary windows python shell cmd exe azure cli extensions azure devops additional context
| 0
|
36,641
| 8,047,556,412
|
IssuesEvent
|
2018-08-01 01:25:40
|
cakephp/cakephp
|
https://api.github.com/repos/cakephp/cakephp
|
closed
|
Cannot issue HTTPS request via Proxy using HttpClient
|
Defect http
|
This is a (multiple allowed):
* [x] bug
* [ ] enhancement
* [ ] feature-discussion (RFC)
Cakephp 3.4.5
```
config:
"proxy" => [
"proxy" => "pl3.nordvpn.com:80"
"username" => "xx",
"password" => "xx"
]
$client=new HttpClient($config);
$client->get('http://api.ipify.org'); // works, returns proxied ip
$client->get('https://api.ipify.org'); // does not work
```
This is respone object for https call
```
object(Cake\Http\Client\Response) {
[protected] code => (int) 400
[protected] reasonPhrase => 'Bad Request'
[protected] _xml => null
[protected] _json => null
[protected] _exposedProperties => [
'cookies' => '_cookies',
'body' => '_getBody',
'code' => 'code',
'json' => '_getJson',
'xml' => '_getXml',
'headers' => '_getHeaders'
]
[protected] _cookies => []
[protected] _body => null
[protected] headers => [
'Connection' => [
(int) 0 => 'close'
],
'Server' => [
(int) 0 => 'Cowboy'
],
'Date' => [
(int) 0 => 'Fri, 30 Jun 2017 12:21:45 GMT'
],
'Content-Length' => [
(int) 0 => '0'
]
]
[protected] headerNames => [
'connection' => 'Connection',
'server' => 'Server',
'date' => 'Date',
'content-length' => 'Content-Length'
]
[private] protocol => '1.1'
[private] stream => object(Zend\Diactoros\Stream) {
[protected] resource => resource
[protected] stream => 'php://memory'
}
}
```
Response body is empty.
|
1.0
|
Cannot issue HTTPS request via Proxy using HttpClient - This is a (multiple allowed):
* [x] bug
* [ ] enhancement
* [ ] feature-discussion (RFC)
Cakephp 3.4.5
```
config:
"proxy" => [
"proxy" => "pl3.nordvpn.com:80"
"username" => "xx",
"password" => "xx"
]
$client=new HttpClient($config);
$client->get('http://api.ipify.org'); // works, returns proxied ip
$client->get('https://api.ipify.org'); // does not work
```
This is respone object for https call
```
object(Cake\Http\Client\Response) {
[protected] code => (int) 400
[protected] reasonPhrase => 'Bad Request'
[protected] _xml => null
[protected] _json => null
[protected] _exposedProperties => [
'cookies' => '_cookies',
'body' => '_getBody',
'code' => 'code',
'json' => '_getJson',
'xml' => '_getXml',
'headers' => '_getHeaders'
]
[protected] _cookies => []
[protected] _body => null
[protected] headers => [
'Connection' => [
(int) 0 => 'close'
],
'Server' => [
(int) 0 => 'Cowboy'
],
'Date' => [
(int) 0 => 'Fri, 30 Jun 2017 12:21:45 GMT'
],
'Content-Length' => [
(int) 0 => '0'
]
]
[protected] headerNames => [
'connection' => 'Connection',
'server' => 'Server',
'date' => 'Date',
'content-length' => 'Content-Length'
]
[private] protocol => '1.1'
[private] stream => object(Zend\Diactoros\Stream) {
[protected] resource => resource
[protected] stream => 'php://memory'
}
}
```
Response body is empty.
|
defect
|
cannot issue https request via proxy using httpclient this is a multiple allowed bug enhancement feature discussion rfc cakephp config proxy proxy nordvpn com username xx password xx client new httpclient config client get works returns proxied ip client get does not work this is respone object for https call object cake http client response code int reasonphrase bad request xml null json null exposedproperties cookies cookies body getbody code code json getjson xml getxml headers getheaders cookies body null headers connection int close server int cowboy date int fri jun gmt content length int headernames connection connection server server date date content length content length protocol stream object zend diactoros stream resource resource stream php memory response body is empty
| 1
|
31,893
| 6,657,392,523
|
IssuesEvent
|
2017-09-30 04:46:36
|
energicryptocurrency/energi
|
https://api.github.com/repos/energicryptocurrency/energi
|
opened
|
Dash logo in background of energi-qt wallet
|
Defect Required for Main Net Small change User Interface
|
There is still a Dash logo faintly in the background of the energi-qt wallet.
<img width="997" alt="screen shot 2017-09-28 at 22 43 16" src="https://user-images.githubusercontent.com/5231832/31042551-04bf3c4a-a568-11e7-94db-163b779ef55b.png">
|
1.0
|
Dash logo in background of energi-qt wallet - There is still a Dash logo faintly in the background of the energi-qt wallet.
<img width="997" alt="screen shot 2017-09-28 at 22 43 16" src="https://user-images.githubusercontent.com/5231832/31042551-04bf3c4a-a568-11e7-94db-163b779ef55b.png">
|
defect
|
dash logo in background of energi qt wallet there is still a dash logo faintly in the background of the energi qt wallet img width alt screen shot at src
| 1
|
34,829
| 7,460,802,037
|
IssuesEvent
|
2018-03-30 21:26:42
|
kerdokullamae/test_koik_issued
|
https://api.github.com/repos/kerdokullamae/test_koik_issued
|
closed
|
Täpsem otsing - tulemuste sorteerimine Leidandmete järgi kohati vigane
|
C: AIS P: highest R: fixed T: defect
|
**Reported by maiu pevkur on 21 Mar 2017 09:12 UTC**
Tehes Täpsemas otsingus Leidandmete alusel päringu, nt ERA.957.8.*, ERA.957.9.*, VAMA.413.1.* ei toimi Leidandmete veeru järgi sorteerimine (mõlemat pidi) õigesti. Vt kohe kõigi näidete puhul esimesel tulemuste lehel (vahet pole, mitu tulemust lehel valida)on vale järjestus näha. Nt http://www.dev-ais-web.arhiiv.ee/et/description_unit/list/?filter%5Btitle%5D=&filter%5BarchiveUnitId%5D=&filter%5Bfns%5D=VAMA.413.1.*&filter%5BoriginalRefCode%5D=&filter%5BlevelId%5D=&filter%5BeraId%5D=&filter%5BresultsPerPage%5D=10&filter%5BdigitizationId%5D=ALL&filter%5BsubjectAreaId%5D=&filter%5BpersonId%5D=&filter%5BadminUnitSwLon%5D=&filter%5BadminUnitSwLat%5D=&filter%5BadminUnitNeLon%5D=&filter%5BadminUnitNeLat%5D=&filter%5BadminUnitRelation%5D=incl Tundub, et probleem on just siis, kui üks päringutingimustest on Leidandmed. Kui teha päring nt Pealkirja järgi ja siis Leidandmete veeru järgi sorteerida, probleeme nagu ei ole paistnud.
|
1.0
|
Täpsem otsing - tulemuste sorteerimine Leidandmete järgi kohati vigane - **Reported by maiu pevkur on 21 Mar 2017 09:12 UTC**
Tehes Täpsemas otsingus Leidandmete alusel päringu, nt ERA.957.8.*, ERA.957.9.*, VAMA.413.1.* ei toimi Leidandmete veeru järgi sorteerimine (mõlemat pidi) õigesti. Vt kohe kõigi näidete puhul esimesel tulemuste lehel (vahet pole, mitu tulemust lehel valida)on vale järjestus näha. Nt http://www.dev-ais-web.arhiiv.ee/et/description_unit/list/?filter%5Btitle%5D=&filter%5BarchiveUnitId%5D=&filter%5Bfns%5D=VAMA.413.1.*&filter%5BoriginalRefCode%5D=&filter%5BlevelId%5D=&filter%5BeraId%5D=&filter%5BresultsPerPage%5D=10&filter%5BdigitizationId%5D=ALL&filter%5BsubjectAreaId%5D=&filter%5BpersonId%5D=&filter%5BadminUnitSwLon%5D=&filter%5BadminUnitSwLat%5D=&filter%5BadminUnitNeLon%5D=&filter%5BadminUnitNeLat%5D=&filter%5BadminUnitRelation%5D=incl Tundub, et probleem on just siis, kui üks päringutingimustest on Leidandmed. Kui teha päring nt Pealkirja järgi ja siis Leidandmete veeru järgi sorteerida, probleeme nagu ei ole paistnud.
|
defect
|
täpsem otsing tulemuste sorteerimine leidandmete järgi kohati vigane reported by maiu pevkur on mar utc tehes täpsemas otsingus leidandmete alusel päringu nt era era vama ei toimi leidandmete veeru järgi sorteerimine mõlemat pidi õigesti vt kohe kõigi näidete puhul esimesel tulemuste lehel vahet pole mitu tulemust lehel valida on vale järjestus näha nt tundub et probleem on just siis kui üks päringutingimustest on leidandmed kui teha päring nt pealkirja järgi ja siis leidandmete veeru järgi sorteerida probleeme nagu ei ole paistnud
| 1
|
57,215
| 15,726,736,778
|
IssuesEvent
|
2021-03-29 11:44:38
|
danmar/testissues
|
https://api.github.com/repos/danmar/testissues
|
opened
|
"++" is changed into two tokens by tokenizer, while it should be only a single token (Trac #101)
|
Incomplete Migration Migrated from Trac Other defect noone
|
Migrated from https://trac.cppcheck.net/ticket/101
```json
{
"status": "closed",
"changetime": "2009-02-14T10:16:10",
"description": "Test case: TestSimplifyTokens::double_plus",
"reporter": "aggro80",
"cc": "",
"resolution": "fixed",
"_ts": "1234606570000000",
"component": "Other",
"summary": "\"++\" is changed into two tokens by tokenizer, while it should be only a single token",
"priority": "",
"keywords": "",
"time": "2009-02-12T20:34:28",
"milestone": "1.29",
"owner": "noone",
"type": "defect"
}
```
|
1.0
|
"++" is changed into two tokens by tokenizer, while it should be only a single token (Trac #101) - Migrated from https://trac.cppcheck.net/ticket/101
```json
{
"status": "closed",
"changetime": "2009-02-14T10:16:10",
"description": "Test case: TestSimplifyTokens::double_plus",
"reporter": "aggro80",
"cc": "",
"resolution": "fixed",
"_ts": "1234606570000000",
"component": "Other",
"summary": "\"++\" is changed into two tokens by tokenizer, while it should be only a single token",
"priority": "",
"keywords": "",
"time": "2009-02-12T20:34:28",
"milestone": "1.29",
"owner": "noone",
"type": "defect"
}
```
|
defect
|
is changed into two tokens by tokenizer while it should be only a single token trac migrated from json status closed changetime description test case testsimplifytokens double plus reporter cc resolution fixed ts component other summary is changed into two tokens by tokenizer while it should be only a single token priority keywords time milestone owner noone type defect
| 1
|
157,595
| 19,959,072,519
|
IssuesEvent
|
2022-01-28 05:24:10
|
JeffResc/IP-API-Node.js
|
https://api.github.com/repos/JeffResc/IP-API-Node.js
|
closed
|
CVE-2020-7656 (Medium) detected in jquery-1.7.2.min.js
|
security vulnerability
|
## CVE-2020-7656 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.7.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js</a></p>
<p>Path to dependency file: IP-API-Node.js/node_modules/marked/www/demo.html</p>
<p>Path to vulnerable library: IP-API-Node.js/node_modules/marked/www/demo.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.7.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/JeffResc/IP-API-Node.js/commit/99b7653bfce099be086c1b68c2b7b8499c3d63af">99b7653bfce099be086c1b68c2b7b8499c3d63af</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jquery prior to 1.9.0 allows Cross-site Scripting attacks via the load method. The load method fails to recognize and remove "<script>" HTML tags that contain a whitespace character, i.e: "</script >", which results in the enclosed script logic to be executed.
<p>Publish Date: 2020-05-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7656>CVE-2020-7656</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/rails/jquery-rails/commit/8f601cbfa08749ee5bbd2bffb6e509db9d753568">https://github.com/rails/jquery-rails/commit/8f601cbfa08749ee5bbd2bffb6e509db9d753568</a></p>
<p>Release Date: 2020-05-19</p>
<p>Fix Resolution: jquery-rails - 2.2.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2020-7656 (Medium) detected in jquery-1.7.2.min.js - ## CVE-2020-7656 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.7.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js</a></p>
<p>Path to dependency file: IP-API-Node.js/node_modules/marked/www/demo.html</p>
<p>Path to vulnerable library: IP-API-Node.js/node_modules/marked/www/demo.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.7.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/JeffResc/IP-API-Node.js/commit/99b7653bfce099be086c1b68c2b7b8499c3d63af">99b7653bfce099be086c1b68c2b7b8499c3d63af</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jquery prior to 1.9.0 allows Cross-site Scripting attacks via the load method. The load method fails to recognize and remove "<script>" HTML tags that contain a whitespace character, i.e: "</script >", which results in the enclosed script logic to be executed.
<p>Publish Date: 2020-05-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7656>CVE-2020-7656</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/rails/jquery-rails/commit/8f601cbfa08749ee5bbd2bffb6e509db9d753568">https://github.com/rails/jquery-rails/commit/8f601cbfa08749ee5bbd2bffb6e509db9d753568</a></p>
<p>Release Date: 2020-05-19</p>
<p>Fix Resolution: jquery-rails - 2.2.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file ip api node js node modules marked www demo html path to vulnerable library ip api node js node modules marked www demo html dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch master vulnerability details jquery prior to allows cross site scripting attacks via the load method the load method fails to recognize and remove html tags that contain a whitespace character i e which results in the enclosed script logic to be executed publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery rails step up your open source security game with whitesource
| 0
|
70,165
| 23,027,989,106
|
IssuesEvent
|
2022-07-22 11:07:34
|
scipy/scipy
|
https://api.github.com/repos/scipy/scipy
|
closed
|
BUG: `scipy.optimize.linprog` reports optimal for trivially infeasible MILP
|
defect scipy.optimize
|
### Describe your issue.
In anticipation of the upcoming 1.9.0 release, I've been trying to update [cvxpy](https://github.com/cvxpy/cvxpy) to use SciPy's newly-introduced MILP functionality. I've been working with SciPy `1.9.0rc2`. You can find [my draft fork of cvxpy here](https://github.com/tasseff/cvxpy) and the associated issue [here](https://github.com/cvxpy/cvxpy/issues/1443). While performing cvxpy unit tests, I came across [a MILP problem](https://github.com/cvxpy/cvxpy/blob/8cc75a8616ac4643134e25147033054d92d89951/cvxpy/tests/test_mip_vars.py#L92-L97) of the form
```
Minimize
obj: t
Subject To
c1: y = 0.5
Bounds
0 <= t
General
y
End
```
The problem is clearly infeasible, as `y` cannot be both integer (indicated by the `General` entry) and equal to `0.5`. This would be solved using SciPy's new MILP functionality with the script I've added below. Curiously, the solution status is reported as optimal, although it should clearly be reported as infeasible. (It is even acknowledged as infeasible in the rest of the log.) Replacing the `options` flag with `options={'disp': True, 'presolve': False}` provides the expected result, i.e., infeasibility is proven. This suggests the issue may be with the version of HiGHS used by SciPy, and more specifically, its presolve routine.
Indeed, building from [the HiGHS master branch](https://github.com/ERGO-Code/HiGHS) and solving using the above `.lp` problem provides the correct logging output, i.e., the problem is identified as infeasible. A similar issue raised [here](https://github.com/ERGO-Code/HiGHS/issues/902) suggests that this issue may not have been corrected, but another issue [here](https://github.com/ERGO-Code/HiGHS/issues/907) has been closed. Suffice to say, I think this is a trivial enough example where the correct behavior needs to be ensured by both SciPy and HiGHS. You may want to consider updating the version of HiGHS used for the 1.9.0 release or, if that is not enough, (i) providing a fix within HiGHS or (ii) waiting for this fix before releasing SciPy 1.9.0.
### Reproducing Code Example
```python
import numpy as np
import scipy
res = scipy.optimize.linprog(
c=[1.0, 0.0],
A_eq=[[0.0, 1.0]],
b_eq=[[0.5]],
bounds=[(0.0, None), (None, None)],
integrality=[0, 1],
options={'disp': True})
```
### Error message
```shell
Presolving model
0 rows, 0 cols, 0 nonzeros
0 rows, 0 cols, 0 nonzeros
Presolve: Optimal
WARNING: Untransformed solution with objective 0 is violated by 0.5 for the original model
Solving report
Status Optimal
Primal bound 0
Dual bound 0
Solution status infeasible
0 (objective)
0 (bound viol.)
0.5 (int. viol.)
0 (row viol.)
Timing 0.01 (total)
0.00 (presolve)
0.00 (postsolve)
Nodes 0
LP iterations 0 (total)
0 (strong br.)
0 (separation)
0 (heuristics)
```
### SciPy/NumPy/Python version information
1.9.0rc2 1.22.3 sys.version_info(major=3, minor=9, micro=12, releaselevel='final', serial=0)
|
1.0
|
BUG: `scipy.optimize.linprog` reports optimal for trivially infeasible MILP - ### Describe your issue.
In anticipation of the upcoming 1.9.0 release, I've been trying to update [cvxpy](https://github.com/cvxpy/cvxpy) to use SciPy's newly-introduced MILP functionality. I've been working with SciPy `1.9.0rc2`. You can find [my draft fork of cvxpy here](https://github.com/tasseff/cvxpy) and the associated issue [here](https://github.com/cvxpy/cvxpy/issues/1443). While performing cvxpy unit tests, I came across [a MILP problem](https://github.com/cvxpy/cvxpy/blob/8cc75a8616ac4643134e25147033054d92d89951/cvxpy/tests/test_mip_vars.py#L92-L97) of the form
```
Minimize
obj: t
Subject To
c1: y = 0.5
Bounds
0 <= t
General
y
End
```
The problem is clearly infeasible, as `y` cannot be both integer (indicated by the `General` entry) and equal to `0.5`. This would be solved using SciPy's new MILP functionality with the script I've added below. Curiously, the solution status is reported as optimal, although it should clearly be reported as infeasible. (It is even acknowledged as infeasible in the rest of the log.) Replacing the `options` flag with `options={'disp': True, 'presolve': False}` provides the expected result, i.e., infeasibility is proven. This suggests the issue may be with the version of HiGHS used by SciPy, and more specifically, its presolve routine.
Indeed, building from [the HiGHS master branch](https://github.com/ERGO-Code/HiGHS) and solving using the above `.lp` problem provides the correct logging output, i.e., the problem is identified as infeasible. A similar issue raised [here](https://github.com/ERGO-Code/HiGHS/issues/902) suggests that this issue may not have been corrected, but another issue [here](https://github.com/ERGO-Code/HiGHS/issues/907) has been closed. Suffice to say, I think this is a trivial enough example where the correct behavior needs to be ensured by both SciPy and HiGHS. You may want to consider updating the version of HiGHS used for the 1.9.0 release or, if that is not enough, (i) providing a fix within HiGHS or (ii) waiting for this fix before releasing SciPy 1.9.0.
### Reproducing Code Example
```python
import numpy as np
import scipy
res = scipy.optimize.linprog(
c=[1.0, 0.0],
A_eq=[[0.0, 1.0]],
b_eq=[[0.5]],
bounds=[(0.0, None), (None, None)],
integrality=[0, 1],
options={'disp': True})
```
### Error message
```shell
Presolving model
0 rows, 0 cols, 0 nonzeros
0 rows, 0 cols, 0 nonzeros
Presolve: Optimal
WARNING: Untransformed solution with objective 0 is violated by 0.5 for the original model
Solving report
Status Optimal
Primal bound 0
Dual bound 0
Solution status infeasible
0 (objective)
0 (bound viol.)
0.5 (int. viol.)
0 (row viol.)
Timing 0.01 (total)
0.00 (presolve)
0.00 (postsolve)
Nodes 0
LP iterations 0 (total)
0 (strong br.)
0 (separation)
0 (heuristics)
```
### SciPy/NumPy/Python version information
1.9.0rc2 1.22.3 sys.version_info(major=3, minor=9, micro=12, releaselevel='final', serial=0)
|
defect
|
bug scipy optimize linprog reports optimal for trivially infeasible milp describe your issue in anticipation of the upcoming release i ve been trying to update to use scipy s newly introduced milp functionality i ve been working with scipy you can find and the associated issue while performing cvxpy unit tests i came across of the form minimize obj t subject to y bounds t general y end the problem is clearly infeasible as y cannot be both integer indicated by the general entry and equal to this would be solved using scipy s new milp functionality with the script i ve added below curiously the solution status is reported as optimal although it should clearly be reported as infeasible it is even acknowledged as infeasible in the rest of the log replacing the options flag with options disp true presolve false provides the expected result i e infeasibility is proven this suggests the issue may be with the version of highs used by scipy and more specifically its presolve routine indeed building from and solving using the above lp problem provides the correct logging output i e the problem is identified as infeasible a similar issue raised suggests that this issue may not have been corrected but another issue has been closed suffice to say i think this is a trivial enough example where the correct behavior needs to be ensured by both scipy and highs you may want to consider updating the version of highs used for the release or if that is not enough i providing a fix within highs or ii waiting for this fix before releasing scipy reproducing code example python import numpy as np import scipy res scipy optimize linprog c a eq b eq bounds integrality options disp true error message shell presolving model rows cols nonzeros rows cols nonzeros presolve optimal warning untransformed solution with objective is violated by for the original model solving report status optimal primal bound dual bound solution status infeasible objective bound viol int viol row viol timing total presolve postsolve nodes lp iterations total strong br separation heuristics scipy numpy python version information sys version info major minor micro releaselevel final serial
| 1
|
146,018
| 19,393,779,343
|
IssuesEvent
|
2021-12-18 01:02:41
|
samq-ghdemo/Webgoat8
|
https://api.github.com/repos/samq-ghdemo/Webgoat8
|
opened
|
CVE-2021-42550 (Medium) detected in logback-classic-1.2.3.jar
|
security vulnerability
|
## CVE-2021-42550 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>logback-classic-1.2.3.jar</b></p></summary>
<p>logback-classic module</p>
<p>Library home page: <a href="http://logback.qos.ch">http://logback.qos.ch</a></p>
<p>Path to dependency file: Webgoat8/webgoat-container/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/ch/qos/logback/logback-classic/1.2.3/logback-classic-1.2.3.jar,/home/wss-scanner/.m2/repository/ch/qos/logback/logback-classic/1.2.3/logback-classic-1.2.3.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.2.2.RELEASE.jar (Root Library)
- spring-boot-starter-2.2.2.RELEASE.jar
- spring-boot-starter-logging-2.2.2.RELEASE.jar
- :x: **logback-classic-1.2.3.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In logback version 1.2.7 and prior versions, an attacker with the required privileges to edit configurations files could craft a malicious configuration allowing to execute arbitrary code loaded from LDAP servers.
<p>Publish Date: 2021-12-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-42550>CVE-2021-42550</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://logback.qos.ch/news.html">http://logback.qos.ch/news.html</a></p>
<p>Release Date: 2021-12-16</p>
<p>Fix Resolution: ch.qos.logback:logback-classic:1.2.8</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"ch.qos.logback","packageName":"logback-classic","packageVersion":"1.2.3","packageFilePaths":["/webgoat-container/pom.xml","/webwolf/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.2.2.RELEASE;org.springframework.boot:spring-boot-starter:2.2.2.RELEASE;org.springframework.boot:spring-boot-starter-logging:2.2.2.RELEASE;ch.qos.logback:logback-classic:1.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"ch.qos.logback:logback-classic:1.2.8","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-42550","vulnerabilityDetails":"In logback version 1.2.7 and prior versions, an attacker with the required privileges to edit configurations files could craft a malicious configuration allowing to execute arbitrary code loaded from LDAP servers.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-42550","cvss3Severity":"medium","cvss3Score":"6.6","cvss3Metrics":{"A":"High","AC":"High","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2021-42550 (Medium) detected in logback-classic-1.2.3.jar - ## CVE-2021-42550 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>logback-classic-1.2.3.jar</b></p></summary>
<p>logback-classic module</p>
<p>Library home page: <a href="http://logback.qos.ch">http://logback.qos.ch</a></p>
<p>Path to dependency file: Webgoat8/webgoat-container/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/ch/qos/logback/logback-classic/1.2.3/logback-classic-1.2.3.jar,/home/wss-scanner/.m2/repository/ch/qos/logback/logback-classic/1.2.3/logback-classic-1.2.3.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.2.2.RELEASE.jar (Root Library)
- spring-boot-starter-2.2.2.RELEASE.jar
- spring-boot-starter-logging-2.2.2.RELEASE.jar
- :x: **logback-classic-1.2.3.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In logback version 1.2.7 and prior versions, an attacker with the required privileges to edit configurations files could craft a malicious configuration allowing to execute arbitrary code loaded from LDAP servers.
<p>Publish Date: 2021-12-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-42550>CVE-2021-42550</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://logback.qos.ch/news.html">http://logback.qos.ch/news.html</a></p>
<p>Release Date: 2021-12-16</p>
<p>Fix Resolution: ch.qos.logback:logback-classic:1.2.8</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"ch.qos.logback","packageName":"logback-classic","packageVersion":"1.2.3","packageFilePaths":["/webgoat-container/pom.xml","/webwolf/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.2.2.RELEASE;org.springframework.boot:spring-boot-starter:2.2.2.RELEASE;org.springframework.boot:spring-boot-starter-logging:2.2.2.RELEASE;ch.qos.logback:logback-classic:1.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"ch.qos.logback:logback-classic:1.2.8","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-42550","vulnerabilityDetails":"In logback version 1.2.7 and prior versions, an attacker with the required privileges to edit configurations files could craft a malicious configuration allowing to execute arbitrary code loaded from LDAP servers.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-42550","cvss3Severity":"medium","cvss3Score":"6.6","cvss3Metrics":{"A":"High","AC":"High","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> -->
|
non_defect
|
cve medium detected in logback classic jar cve medium severity vulnerability vulnerable library logback classic jar logback classic module library home page a href path to dependency file webgoat container pom xml path to vulnerable library home wss scanner repository ch qos logback logback classic logback classic jar home wss scanner repository ch qos logback logback classic logback classic jar dependency hierarchy spring boot starter web release jar root library spring boot starter release jar spring boot starter logging release jar x logback classic jar vulnerable library found in base branch main vulnerability details in logback version and prior versions an attacker with the required privileges to edit configurations files could craft a malicious configuration allowing to execute arbitrary code loaded from ldap servers publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ch qos logback logback classic isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org springframework boot spring boot starter web release org springframework boot spring boot starter release org springframework boot spring boot starter logging release ch qos logback logback classic isminimumfixversionavailable true minimumfixversion ch qos logback logback classic isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails in logback version and prior versions an attacker with the required privileges to edit configurations files could craft a malicious configuration allowing to execute arbitrary code loaded from ldap servers vulnerabilityurl
| 0
|
163,923
| 20,364,279,852
|
IssuesEvent
|
2022-02-21 02:28:34
|
delaval-htps/ProjetDevJava
|
https://api.github.com/repos/delaval-htps/ProjetDevJava
|
opened
|
CVE-2021-3664 (Medium) detected in url-parse-1.4.7.tgz
|
security vulnerability
|
## CVE-2021-3664 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.4.7.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz</a></p>
<p>Path to dependency file: /AppAngular/package.json</p>
<p>Path to vulnerable library: /AppAngular/node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.1001.7.tgz (Root Library)
- webpack-dev-server-3.11.0.tgz
- sockjs-client-1.4.0.tgz
- :x: **url-parse-1.4.7.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
url-parse is vulnerable to URL Redirection to Untrusted Site
<p>Publish Date: 2021-07-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3664>CVE-2021-3664</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-3664">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-3664</a></p>
<p>Release Date: 2021-07-26</p>
<p>Fix Resolution (url-parse): 1.5.2</p>
<p>Direct dependency fix Resolution (@angular-devkit/build-angular): 0.1002.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2021-3664 (Medium) detected in url-parse-1.4.7.tgz - ## CVE-2021-3664 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.4.7.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz</a></p>
<p>Path to dependency file: /AppAngular/package.json</p>
<p>Path to vulnerable library: /AppAngular/node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.1001.7.tgz (Root Library)
- webpack-dev-server-3.11.0.tgz
- sockjs-client-1.4.0.tgz
- :x: **url-parse-1.4.7.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
url-parse is vulnerable to URL Redirection to Untrusted Site
<p>Publish Date: 2021-07-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3664>CVE-2021-3664</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-3664">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-3664</a></p>
<p>Release Date: 2021-07-26</p>
<p>Fix Resolution (url-parse): 1.5.2</p>
<p>Direct dependency fix Resolution (@angular-devkit/build-angular): 0.1002.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve medium detected in url parse tgz cve medium severity vulnerability vulnerable library url parse tgz small footprint url parser that works seamlessly across node js and browser environments library home page a href path to dependency file appangular package json path to vulnerable library appangular node modules url parse package json dependency hierarchy build angular tgz root library webpack dev server tgz sockjs client tgz x url parse tgz vulnerable library found in base branch master vulnerability details url parse is vulnerable to url redirection to untrusted site publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution url parse direct dependency fix resolution angular devkit build angular step up your open source security game with whitesource
| 0
|
347,351
| 31,160,257,076
|
IssuesEvent
|
2023-08-16 15:31:11
|
damccorm/beam
|
https://api.github.com/repos/damccorm/beam
|
closed
|
[Failing Test]:
|
bug flaky tests P2
|
### What happened?
af
### Issue Failure
Failure: Test is flaky
### Issue Priority
Priority: 2 (backlog / disabled test but we think the product is healthy)
### Issue Components
- [ ] Component: Python
- [ ] Component: Java
- [X] Component: Go
- [ ] Component: Typescript
- [ ] Component: IO connector
- [ ] Component: Beam examples
- [ ] Component: Beam playground
- [ ] Component: Beam katas
- [ ] Component: Website
- [ ] Component: Spark Runner
- [ ] Component: Flink Runner
- [ ] Component: Samza Runner
- [ ] Component: Twister2 Runner
- [ ] Component: Hazelcast Jet Runner
- [ ] Component: Google Cloud Dataflow Runner
|
1.0
|
[Failing Test]: - ### What happened?
af
### Issue Failure
Failure: Test is flaky
### Issue Priority
Priority: 2 (backlog / disabled test but we think the product is healthy)
### Issue Components
- [ ] Component: Python
- [ ] Component: Java
- [X] Component: Go
- [ ] Component: Typescript
- [ ] Component: IO connector
- [ ] Component: Beam examples
- [ ] Component: Beam playground
- [ ] Component: Beam katas
- [ ] Component: Website
- [ ] Component: Spark Runner
- [ ] Component: Flink Runner
- [ ] Component: Samza Runner
- [ ] Component: Twister2 Runner
- [ ] Component: Hazelcast Jet Runner
- [ ] Component: Google Cloud Dataflow Runner
|
non_defect
|
what happened af issue failure failure test is flaky issue priority priority backlog disabled test but we think the product is healthy issue components component python component java component go component typescript component io connector component beam examples component beam playground component beam katas component website component spark runner component flink runner component samza runner component runner component hazelcast jet runner component google cloud dataflow runner
| 0
|
660,099
| 21,951,590,115
|
IssuesEvent
|
2022-05-24 08:25:15
|
googleapis/java-dataproc
|
https://api.github.com/repos/googleapis/java-dataproc
|
closed
|
SubmitJobTest: submitJobTest failed
|
type: bug priority: p1 api: dataproc flakybot: issue
|
Note: #849 was also for this test, but it was closed more than 10 days ago. So, I didn't mark it flaky.
----
commit: b5d889e6e485c70f5cd893a0355a65b2a76bbdb7
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/89f05561-4549-4153-ae9f-18794f81eeb7), [Sponge](http://sponge2/89f05561-4549-4153-ae9f-18794f81eeb7)
status: failed
<details><summary>Test output</summary><br><pre>java.util.concurrent.ExecutionException: com.google.api.gax.rpc.InvalidArgumentException: Operation with name "projects/java-docs-samples-testing/regions/us-central1/operations/ab30251d-2096-4bed-8279-5c8a92cc20ac" failed with status = GrpcStatusCode{transportCode=INVALID_ARGUMENT} and message = The resource 'projects/java-docs-samples-testing/regions/us-central1/subnetworks/default' is not ready
at com.google.common.util.concurrent.AbstractFuture.getDoneValue(AbstractFuture.java:588)
at com.google.common.util.concurrent.AbstractFuture.get(AbstractFuture.java:567)
at com.google.common.util.concurrent.FluentFuture$TrustedFuture.get(FluentFuture.java:91)
at com.google.common.util.concurrent.ForwardingFuture.get(ForwardingFuture.java:66)
at com.google.api.gax.longrunning.OperationFutureImpl.get(OperationFutureImpl.java:125)
at SubmitJobTest.setUp(SubmitJobTest.java:95)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:59)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:56)
at org.junit.internal.runners.statements.RunBefores.invokeMethod(RunBefores.java:33)
at org.junit.internal.runners.statements.RunBefores.evaluate(RunBefores.java:24)
at org.junit.internal.runners.statements.RunAfters.evaluate(RunAfters.java:27)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.BlockJUnit4ClassRunner$1.evaluate(BlockJUnit4ClassRunner.java:100)
at org.junit.runners.ParentRunner.runLeaf(ParentRunner.java:366)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:103)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:63)
at org.junit.runners.ParentRunner$4.run(ParentRunner.java:331)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:79)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:329)
at org.junit.runners.ParentRunner.access$100(ParentRunner.java:66)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:293)
at org.junit.internal.runners.statements.RunBefores.evaluate(RunBefores.java:26)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.ParentRunner.run(ParentRunner.java:413)
at org.apache.maven.surefire.junit4.JUnit4Provider.execute(JUnit4Provider.java:364)
at org.apache.maven.surefire.junit4.JUnit4Provider.executeWithRerun(JUnit4Provider.java:272)
at org.apache.maven.surefire.junit4.JUnit4Provider.executeTestSet(JUnit4Provider.java:237)
at org.apache.maven.surefire.junit4.JUnit4Provider.invoke(JUnit4Provider.java:158)
at org.apache.maven.surefire.booter.ForkedBooter.runSuitesInProcess(ForkedBooter.java:428)
at org.apache.maven.surefire.booter.ForkedBooter.execute(ForkedBooter.java:162)
at org.apache.maven.surefire.booter.ForkedBooter.run(ForkedBooter.java:562)
at org.apache.maven.surefire.booter.ForkedBooter.main(ForkedBooter.java:548)
Caused by: com.google.api.gax.rpc.InvalidArgumentException: Operation with name "projects/java-docs-samples-testing/regions/us-central1/operations/ab30251d-2096-4bed-8279-5c8a92cc20ac" failed with status = GrpcStatusCode{transportCode=INVALID_ARGUMENT} and message = The resource 'projects/java-docs-samples-testing/regions/us-central1/subnetworks/default' is not ready
at com.google.api.gax.rpc.ApiExceptionFactory.createException(ApiExceptionFactory.java:52)
at com.google.api.gax.grpc.ProtoOperationTransformers$ResponseTransformer.apply(ProtoOperationTransformers.java:55)
at com.google.api.gax.grpc.ProtoOperationTransformers$ResponseTransformer.apply(ProtoOperationTransformers.java:44)
at com.google.api.core.ApiFutures$ApiFunctionToGuavaFunction.apply(ApiFutures.java:239)
at com.google.common.util.concurrent.AbstractTransformFuture$TransformFuture.doTransform(AbstractTransformFuture.java:250)
at com.google.common.util.concurrent.AbstractTransformFuture$TransformFuture.doTransform(AbstractTransformFuture.java:240)
at com.google.common.util.concurrent.AbstractTransformFuture.run(AbstractTransformFuture.java:122)
at com.google.common.util.concurrent.DirectExecutor.execute(DirectExecutor.java:31)
at com.google.common.util.concurrent.AbstractFuture.executeListener(AbstractFuture.java:1270)
at com.google.common.util.concurrent.AbstractFuture.complete(AbstractFuture.java:1038)
at com.google.common.util.concurrent.AbstractFuture.set(AbstractFuture.java:783)
at com.google.api.gax.retrying.BasicRetryingFuture.handleAttempt(BasicRetryingFuture.java:203)
at com.google.api.gax.retrying.CallbackChainRetryingFuture$AttemptCompletionListener.handle(CallbackChainRetryingFuture.java:135)
at com.google.api.gax.retrying.CallbackChainRetryingFuture$AttemptCompletionListener.run(CallbackChainRetryingFuture.java:115)
at com.google.common.util.concurrent.DirectExecutor.execute(DirectExecutor.java:31)
at com.google.common.util.concurrent.AbstractFuture.executeListener(AbstractFuture.java:1270)
at com.google.common.util.concurrent.AbstractFuture.complete(AbstractFuture.java:1038)
at com.google.common.util.concurrent.AbstractFuture.set(AbstractFuture.java:783)
at com.google.common.util.concurrent.AbstractTransformFuture$TransformFuture.setResult(AbstractTransformFuture.java:255)
at com.google.common.util.concurrent.AbstractTransformFuture.run(AbstractTransformFuture.java:167)
at com.google.common.util.concurrent.DirectExecutor.execute(DirectExecutor.java:31)
at com.google.common.util.concurrent.AbstractFuture.executeListener(AbstractFuture.java:1270)
at com.google.common.util.concurrent.AbstractFuture.complete(AbstractFuture.java:1038)
at com.google.common.util.concurrent.AbstractFuture.set(AbstractFuture.java:783)
at com.google.api.gax.retrying.BasicRetryingFuture.handleAttempt(BasicRetryingFuture.java:203)
at com.google.api.gax.retrying.CallbackChainRetryingFuture$AttemptCompletionListener.handle(CallbackChainRetryingFuture.java:135)
at com.google.api.gax.retrying.CallbackChainRetryingFuture$AttemptCompletionListener.run(CallbackChainRetryingFuture.java:115)
at com.google.common.util.concurrent.DirectExecutor.execute(DirectExecutor.java:31)
at com.google.common.util.concurrent.AbstractFuture.executeListener(AbstractFuture.java:1270)
at com.google.common.util.concurrent.AbstractFuture.complete(AbstractFuture.java:1038)
at com.google.common.util.concurrent.AbstractFuture.set(AbstractFuture.java:783)
at com.google.api.core.AbstractApiFuture$InternalSettableFuture.set(AbstractApiFuture.java:89)
at com.google.api.core.AbstractApiFuture.set(AbstractApiFuture.java:72)
at com.google.api.gax.grpc.GrpcExceptionCallable$ExceptionTransformingFuture.onSuccess(GrpcExceptionCallable.java:88)
at com.google.api.core.ApiFutures$1.onSuccess(ApiFutures.java:72)
at com.google.common.util.concurrent.Futures$CallbackListener.run(Futures.java:1138)
at com.google.common.util.concurrent.DirectExecutor.execute(DirectExecutor.java:31)
at com.google.common.util.concurrent.AbstractFuture.executeListener(AbstractFuture.java:1270)
at com.google.common.util.concurrent.AbstractFuture.complete(AbstractFuture.java:1038)
at com.google.common.util.concurrent.AbstractFuture.set(AbstractFuture.java:783)
at io.grpc.stub.ClientCalls$GrpcFuture.set(ClientCalls.java:567)
at io.grpc.stub.ClientCalls$UnaryStreamToFuture.onClose(ClientCalls.java:540)
at io.grpc.PartialForwardingClientCallListener.onClose(PartialForwardingClientCallListener.java:39)
at io.grpc.ForwardingClientCallListener.onClose(ForwardingClientCallListener.java:23)
at io.grpc.ForwardingClientCallListener$SimpleForwardingClientCallListener.onClose(ForwardingClientCallListener.java:40)
at com.google.api.gax.grpc.ChannelPool$ReleasingClientCall$1.onClose(ChannelPool.java:535)
at io.grpc.internal.ClientCallImpl.closeObserver(ClientCallImpl.java:562)
at io.grpc.internal.ClientCallImpl.access$300(ClientCallImpl.java:70)
at io.grpc.internal.ClientCallImpl$ClientStreamListenerImpl$1StreamClosed.runInternal(ClientCallImpl.java:743)
at io.grpc.internal.ClientCallImpl$ClientStreamListenerImpl$1StreamClosed.runInContext(ClientCallImpl.java:722)
at io.grpc.internal.ContextRunnable.run(ContextRunnable.java:37)
at io.grpc.internal.SerializingExecutor.run(SerializingExecutor.java:133)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
at java.lang.Thread.run(Thread.java:750)
</pre></details>
|
1.0
|
SubmitJobTest: submitJobTest failed - Note: #849 was also for this test, but it was closed more than 10 days ago. So, I didn't mark it flaky.
----
commit: b5d889e6e485c70f5cd893a0355a65b2a76bbdb7
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/89f05561-4549-4153-ae9f-18794f81eeb7), [Sponge](http://sponge2/89f05561-4549-4153-ae9f-18794f81eeb7)
status: failed
<details><summary>Test output</summary><br><pre>java.util.concurrent.ExecutionException: com.google.api.gax.rpc.InvalidArgumentException: Operation with name "projects/java-docs-samples-testing/regions/us-central1/operations/ab30251d-2096-4bed-8279-5c8a92cc20ac" failed with status = GrpcStatusCode{transportCode=INVALID_ARGUMENT} and message = The resource 'projects/java-docs-samples-testing/regions/us-central1/subnetworks/default' is not ready
at com.google.common.util.concurrent.AbstractFuture.getDoneValue(AbstractFuture.java:588)
at com.google.common.util.concurrent.AbstractFuture.get(AbstractFuture.java:567)
at com.google.common.util.concurrent.FluentFuture$TrustedFuture.get(FluentFuture.java:91)
at com.google.common.util.concurrent.ForwardingFuture.get(ForwardingFuture.java:66)
at com.google.api.gax.longrunning.OperationFutureImpl.get(OperationFutureImpl.java:125)
at SubmitJobTest.setUp(SubmitJobTest.java:95)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:59)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:56)
at org.junit.internal.runners.statements.RunBefores.invokeMethod(RunBefores.java:33)
at org.junit.internal.runners.statements.RunBefores.evaluate(RunBefores.java:24)
at org.junit.internal.runners.statements.RunAfters.evaluate(RunAfters.java:27)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.BlockJUnit4ClassRunner$1.evaluate(BlockJUnit4ClassRunner.java:100)
at org.junit.runners.ParentRunner.runLeaf(ParentRunner.java:366)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:103)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:63)
at org.junit.runners.ParentRunner$4.run(ParentRunner.java:331)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:79)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:329)
at org.junit.runners.ParentRunner.access$100(ParentRunner.java:66)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:293)
at org.junit.internal.runners.statements.RunBefores.evaluate(RunBefores.java:26)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.ParentRunner.run(ParentRunner.java:413)
at org.apache.maven.surefire.junit4.JUnit4Provider.execute(JUnit4Provider.java:364)
at org.apache.maven.surefire.junit4.JUnit4Provider.executeWithRerun(JUnit4Provider.java:272)
at org.apache.maven.surefire.junit4.JUnit4Provider.executeTestSet(JUnit4Provider.java:237)
at org.apache.maven.surefire.junit4.JUnit4Provider.invoke(JUnit4Provider.java:158)
at org.apache.maven.surefire.booter.ForkedBooter.runSuitesInProcess(ForkedBooter.java:428)
at org.apache.maven.surefire.booter.ForkedBooter.execute(ForkedBooter.java:162)
at org.apache.maven.surefire.booter.ForkedBooter.run(ForkedBooter.java:562)
at org.apache.maven.surefire.booter.ForkedBooter.main(ForkedBooter.java:548)
Caused by: com.google.api.gax.rpc.InvalidArgumentException: Operation with name "projects/java-docs-samples-testing/regions/us-central1/operations/ab30251d-2096-4bed-8279-5c8a92cc20ac" failed with status = GrpcStatusCode{transportCode=INVALID_ARGUMENT} and message = The resource 'projects/java-docs-samples-testing/regions/us-central1/subnetworks/default' is not ready
at com.google.api.gax.rpc.ApiExceptionFactory.createException(ApiExceptionFactory.java:52)
at com.google.api.gax.grpc.ProtoOperationTransformers$ResponseTransformer.apply(ProtoOperationTransformers.java:55)
at com.google.api.gax.grpc.ProtoOperationTransformers$ResponseTransformer.apply(ProtoOperationTransformers.java:44)
at com.google.api.core.ApiFutures$ApiFunctionToGuavaFunction.apply(ApiFutures.java:239)
at com.google.common.util.concurrent.AbstractTransformFuture$TransformFuture.doTransform(AbstractTransformFuture.java:250)
at com.google.common.util.concurrent.AbstractTransformFuture$TransformFuture.doTransform(AbstractTransformFuture.java:240)
at com.google.common.util.concurrent.AbstractTransformFuture.run(AbstractTransformFuture.java:122)
at com.google.common.util.concurrent.DirectExecutor.execute(DirectExecutor.java:31)
at com.google.common.util.concurrent.AbstractFuture.executeListener(AbstractFuture.java:1270)
at com.google.common.util.concurrent.AbstractFuture.complete(AbstractFuture.java:1038)
at com.google.common.util.concurrent.AbstractFuture.set(AbstractFuture.java:783)
at com.google.api.gax.retrying.BasicRetryingFuture.handleAttempt(BasicRetryingFuture.java:203)
at com.google.api.gax.retrying.CallbackChainRetryingFuture$AttemptCompletionListener.handle(CallbackChainRetryingFuture.java:135)
at com.google.api.gax.retrying.CallbackChainRetryingFuture$AttemptCompletionListener.run(CallbackChainRetryingFuture.java:115)
at com.google.common.util.concurrent.DirectExecutor.execute(DirectExecutor.java:31)
at com.google.common.util.concurrent.AbstractFuture.executeListener(AbstractFuture.java:1270)
at com.google.common.util.concurrent.AbstractFuture.complete(AbstractFuture.java:1038)
at com.google.common.util.concurrent.AbstractFuture.set(AbstractFuture.java:783)
at com.google.common.util.concurrent.AbstractTransformFuture$TransformFuture.setResult(AbstractTransformFuture.java:255)
at com.google.common.util.concurrent.AbstractTransformFuture.run(AbstractTransformFuture.java:167)
at com.google.common.util.concurrent.DirectExecutor.execute(DirectExecutor.java:31)
at com.google.common.util.concurrent.AbstractFuture.executeListener(AbstractFuture.java:1270)
at com.google.common.util.concurrent.AbstractFuture.complete(AbstractFuture.java:1038)
at com.google.common.util.concurrent.AbstractFuture.set(AbstractFuture.java:783)
at com.google.api.gax.retrying.BasicRetryingFuture.handleAttempt(BasicRetryingFuture.java:203)
at com.google.api.gax.retrying.CallbackChainRetryingFuture$AttemptCompletionListener.handle(CallbackChainRetryingFuture.java:135)
at com.google.api.gax.retrying.CallbackChainRetryingFuture$AttemptCompletionListener.run(CallbackChainRetryingFuture.java:115)
at com.google.common.util.concurrent.DirectExecutor.execute(DirectExecutor.java:31)
at com.google.common.util.concurrent.AbstractFuture.executeListener(AbstractFuture.java:1270)
at com.google.common.util.concurrent.AbstractFuture.complete(AbstractFuture.java:1038)
at com.google.common.util.concurrent.AbstractFuture.set(AbstractFuture.java:783)
at com.google.api.core.AbstractApiFuture$InternalSettableFuture.set(AbstractApiFuture.java:89)
at com.google.api.core.AbstractApiFuture.set(AbstractApiFuture.java:72)
at com.google.api.gax.grpc.GrpcExceptionCallable$ExceptionTransformingFuture.onSuccess(GrpcExceptionCallable.java:88)
at com.google.api.core.ApiFutures$1.onSuccess(ApiFutures.java:72)
at com.google.common.util.concurrent.Futures$CallbackListener.run(Futures.java:1138)
at com.google.common.util.concurrent.DirectExecutor.execute(DirectExecutor.java:31)
at com.google.common.util.concurrent.AbstractFuture.executeListener(AbstractFuture.java:1270)
at com.google.common.util.concurrent.AbstractFuture.complete(AbstractFuture.java:1038)
at com.google.common.util.concurrent.AbstractFuture.set(AbstractFuture.java:783)
at io.grpc.stub.ClientCalls$GrpcFuture.set(ClientCalls.java:567)
at io.grpc.stub.ClientCalls$UnaryStreamToFuture.onClose(ClientCalls.java:540)
at io.grpc.PartialForwardingClientCallListener.onClose(PartialForwardingClientCallListener.java:39)
at io.grpc.ForwardingClientCallListener.onClose(ForwardingClientCallListener.java:23)
at io.grpc.ForwardingClientCallListener$SimpleForwardingClientCallListener.onClose(ForwardingClientCallListener.java:40)
at com.google.api.gax.grpc.ChannelPool$ReleasingClientCall$1.onClose(ChannelPool.java:535)
at io.grpc.internal.ClientCallImpl.closeObserver(ClientCallImpl.java:562)
at io.grpc.internal.ClientCallImpl.access$300(ClientCallImpl.java:70)
at io.grpc.internal.ClientCallImpl$ClientStreamListenerImpl$1StreamClosed.runInternal(ClientCallImpl.java:743)
at io.grpc.internal.ClientCallImpl$ClientStreamListenerImpl$1StreamClosed.runInContext(ClientCallImpl.java:722)
at io.grpc.internal.ContextRunnable.run(ContextRunnable.java:37)
at io.grpc.internal.SerializingExecutor.run(SerializingExecutor.java:133)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
at java.lang.Thread.run(Thread.java:750)
</pre></details>
|
non_defect
|
submitjobtest submitjobtest failed note was also for this test but it was closed more than days ago so i didn t mark it flaky commit buildurl status failed test output java util concurrent executionexception com google api gax rpc invalidargumentexception operation with name projects java docs samples testing regions us operations failed with status grpcstatuscode transportcode invalid argument and message the resource projects java docs samples testing regions us subnetworks default is not ready at com google common util concurrent abstractfuture getdonevalue abstractfuture java at com google common util concurrent abstractfuture get abstractfuture java at com google common util concurrent fluentfuture trustedfuture get fluentfuture java at com google common util concurrent forwardingfuture get forwardingfuture java at com google api gax longrunning operationfutureimpl get operationfutureimpl java at submitjobtest setup submitjobtest java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org junit runners model frameworkmethod runreflectivecall frameworkmethod java at org junit internal runners model reflectivecallable run reflectivecallable java at org junit runners model frameworkmethod invokeexplosively frameworkmethod java at org junit internal runners statements runbefores invokemethod runbefores java at org junit internal runners statements runbefores evaluate runbefores java at org junit internal runners statements runafters evaluate runafters java at org junit runners parentrunner evaluate parentrunner java at org junit runners evaluate java at org junit runners parentrunner runleaf parentrunner java at org junit runners runchild java at org junit runners runchild java at org junit runners parentrunner run parentrunner java at org junit runners parentrunner schedule parentrunner java at org junit runners parentrunner runchildren parentrunner java at org junit runners parentrunner access parentrunner java at org junit runners parentrunner evaluate parentrunner java at org junit internal runners statements runbefores evaluate runbefores java at org junit runners parentrunner evaluate parentrunner java at org junit runners parentrunner run parentrunner java at org apache maven surefire execute java at org apache maven surefire executewithrerun java at org apache maven surefire executetestset java at org apache maven surefire invoke java at org apache maven surefire booter forkedbooter runsuitesinprocess forkedbooter java at org apache maven surefire booter forkedbooter execute forkedbooter java at org apache maven surefire booter forkedbooter run forkedbooter java at org apache maven surefire booter forkedbooter main forkedbooter java caused by com google api gax rpc invalidargumentexception operation with name projects java docs samples testing regions us operations failed with status grpcstatuscode transportcode invalid argument and message the resource projects java docs samples testing regions us subnetworks default is not ready at com google api gax rpc apiexceptionfactory createexception apiexceptionfactory java at com google api gax grpc protooperationtransformers responsetransformer apply protooperationtransformers java at com google api gax grpc protooperationtransformers responsetransformer apply protooperationtransformers java at com google api core apifutures apifunctiontoguavafunction apply apifutures java at com google common util concurrent abstracttransformfuture transformfuture dotransform abstracttransformfuture java at com google common util concurrent abstracttransformfuture transformfuture dotransform abstracttransformfuture java at com google common util concurrent abstracttransformfuture run abstracttransformfuture java at com google common util concurrent directexecutor execute directexecutor java at com google common util concurrent abstractfuture executelistener abstractfuture java at com google common util concurrent abstractfuture complete abstractfuture java at com google common util concurrent abstractfuture set abstractfuture java at com google api gax retrying basicretryingfuture handleattempt basicretryingfuture java at com google api gax retrying callbackchainretryingfuture attemptcompletionlistener handle callbackchainretryingfuture java at com google api gax retrying callbackchainretryingfuture attemptcompletionlistener run callbackchainretryingfuture java at com google common util concurrent directexecutor execute directexecutor java at com google common util concurrent abstractfuture executelistener abstractfuture java at com google common util concurrent abstractfuture complete abstractfuture java at com google common util concurrent abstractfuture set abstractfuture java at com google common util concurrent abstracttransformfuture transformfuture setresult abstracttransformfuture java at com google common util concurrent abstracttransformfuture run abstracttransformfuture java at com google common util concurrent directexecutor execute directexecutor java at com google common util concurrent abstractfuture executelistener abstractfuture java at com google common util concurrent abstractfuture complete abstractfuture java at com google common util concurrent abstractfuture set abstractfuture java at com google api gax retrying basicretryingfuture handleattempt basicretryingfuture java at com google api gax retrying callbackchainretryingfuture attemptcompletionlistener handle callbackchainretryingfuture java at com google api gax retrying callbackchainretryingfuture attemptcompletionlistener run callbackchainretryingfuture java at com google common util concurrent directexecutor execute directexecutor java at com google common util concurrent abstractfuture executelistener abstractfuture java at com google common util concurrent abstractfuture complete abstractfuture java at com google common util concurrent abstractfuture set abstractfuture java at com google api core abstractapifuture internalsettablefuture set abstractapifuture java at com google api core abstractapifuture set abstractapifuture java at com google api gax grpc grpcexceptioncallable exceptiontransformingfuture onsuccess grpcexceptioncallable java at com google api core apifutures onsuccess apifutures java at com google common util concurrent futures callbacklistener run futures java at com google common util concurrent directexecutor execute directexecutor java at com google common util concurrent abstractfuture executelistener abstractfuture java at com google common util concurrent abstractfuture complete abstractfuture java at com google common util concurrent abstractfuture set abstractfuture java at io grpc stub clientcalls grpcfuture set clientcalls java at io grpc stub clientcalls unarystreamtofuture onclose clientcalls java at io grpc partialforwardingclientcalllistener onclose partialforwardingclientcalllistener java at io grpc forwardingclientcalllistener onclose forwardingclientcalllistener java at io grpc forwardingclientcalllistener simpleforwardingclientcalllistener onclose forwardingclientcalllistener java at com google api gax grpc channelpool releasingclientcall onclose channelpool java at io grpc internal clientcallimpl closeobserver clientcallimpl java at io grpc internal clientcallimpl access clientcallimpl java at io grpc internal clientcallimpl clientstreamlistenerimpl runinternal clientcallimpl java at io grpc internal clientcallimpl clientstreamlistenerimpl runincontext clientcallimpl java at io grpc internal contextrunnable run contextrunnable java at io grpc internal serializingexecutor run serializingexecutor java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java lang thread run thread java
| 0
|
581,088
| 17,273,185,817
|
IssuesEvent
|
2021-07-22 23:35:20
|
redwoodjs/redwood
|
https://api.github.com/repos/redwoodjs/redwood
|
closed
|
Upgrade to PostCss 8 so that can use later versions of TailwindCss/UI
|
next-release/breaking topic/config v1/priority
|
Currently one has to use a PostCss compatible version of TailwindCss.
```js
"devDependencies": {
"autoprefixer": "9.8.6",
"postcss-loader": "4.0.2",
"tailwindcss": "npm:@tailwindcss/postcss7-compat"
}
}
```
@jtoar I recall you looked into this when creating the Tailwind setup.
@thedavidprice thinks it may have been related to WebPack 4 or 5.
What do you think it would take to upgrade to PostCss 8 and then be able to use the latest TW releases?
@Burnsy is using https://github.com/ben-rogerson/twin.macro and has some issues given it requires 8 with RW requires 7.
|
1.0
|
Upgrade to PostCss 8 so that can use later versions of TailwindCss/UI - Currently one has to use a PostCss compatible version of TailwindCss.
```js
"devDependencies": {
"autoprefixer": "9.8.6",
"postcss-loader": "4.0.2",
"tailwindcss": "npm:@tailwindcss/postcss7-compat"
}
}
```
@jtoar I recall you looked into this when creating the Tailwind setup.
@thedavidprice thinks it may have been related to WebPack 4 or 5.
What do you think it would take to upgrade to PostCss 8 and then be able to use the latest TW releases?
@Burnsy is using https://github.com/ben-rogerson/twin.macro and has some issues given it requires 8 with RW requires 7.
|
non_defect
|
upgrade to postcss so that can use later versions of tailwindcss ui currently one has to use a postcss compatible version of tailwindcss js devdependencies autoprefixer postcss loader tailwindcss npm tailwindcss compat jtoar i recall you looked into this when creating the tailwind setup thedavidprice thinks it may have been related to webpack or what do you think it would take to upgrade to postcss and then be able to use the latest tw releases burnsy is using and has some issues given it requires with rw requires
| 0
|
403,099
| 27,400,182,034
|
IssuesEvent
|
2023-02-28 23:36:37
|
NetAppDocs/ontap
|
https://api.github.com/repos/NetAppDocs/ontap
|
closed
|
Cloud you please consider to add reason why it's reccommend to "not use" auto FlexGroup rebalancing.
|
documentation
|
Page: [Rebalance FlexGroup volumes](https://docs.netapp.com/us-en/ontap/flexgroup/manage-flexgroup-rebalance-task.html)
To whom it may concern,
My customer asked me why recommended "not use flexgroup auto FlexGroup rebalancing" after converting from FlexVol to FlexGroup Volume?
=====================================================================
FlexVol to FlexGroup conversion
It is recommended that you do not use automatic FlexGroup rebalancing after a FlexVol to FlexGroup conversion. Instead, you can use the disruptive retroactive file move feature available in ONTAP 9.10.1 and later, by entering the volume rebalance file-move command. For command syntax, see the volume rebalance file-move start man page.
=====================================================================
I can't find reason on docs or any other materials.
So, Cloud you please consider to add reason of why recommended "not use flexgroup auto FlexGroup rebalancing" for explanation?
Best regards,
|
1.0
|
Cloud you please consider to add reason why it's reccommend to "not use" auto FlexGroup rebalancing. - Page: [Rebalance FlexGroup volumes](https://docs.netapp.com/us-en/ontap/flexgroup/manage-flexgroup-rebalance-task.html)
To whom it may concern,
My customer asked me why recommended "not use flexgroup auto FlexGroup rebalancing" after converting from FlexVol to FlexGroup Volume?
=====================================================================
FlexVol to FlexGroup conversion
It is recommended that you do not use automatic FlexGroup rebalancing after a FlexVol to FlexGroup conversion. Instead, you can use the disruptive retroactive file move feature available in ONTAP 9.10.1 and later, by entering the volume rebalance file-move command. For command syntax, see the volume rebalance file-move start man page.
=====================================================================
I can't find reason on docs or any other materials.
So, Cloud you please consider to add reason of why recommended "not use flexgroup auto FlexGroup rebalancing" for explanation?
Best regards,
|
non_defect
|
cloud you please consider to add reason why it s reccommend to not use auto flexgroup rebalancing page to whom it may concern my customer asked me why recommended not use flexgroup auto flexgroup rebalancing after converting from flexvol to flexgroup volume flexvol to flexgroup conversion it is recommended that you do not use automatic flexgroup rebalancing after a flexvol to flexgroup conversion instead you can use the disruptive retroactive file move feature available in ontap and later by entering the volume rebalance file move command for command syntax see the volume rebalance file move start man page i can t find reason on docs or any other materials so cloud you please consider to add reason of why recommended not use flexgroup auto flexgroup rebalancing for explanation best regards
| 0
|
14,965
| 2,832,400,108
|
IssuesEvent
|
2015-05-25 07:42:58
|
ibus/ibus
|
https://api.github.com/repos/ibus/ibus
|
closed
|
Add tone support to default ibus PinYin Engine (like scim)
|
Component-ibus-pinyin Priority-Medium Type-Defect
|
```
What version of the product are you using? On what operating system?
OS (Linux distributions, UNIX or ...): Ubuntu GNU/Linux
Architecture (i386, x86_64): i386
IBus version: 1.4.9-1ubuntu2
Input method name and version: iBUS Pinyin 1.3.0
This is a feature request.
The current iBUS pinyin engine is missing something which I really liked
from SCIM; and since everyone seems to be migrating to SCIM these days, I'd
love it if this feature were ported.
In SCIM's pinyin program, it is possible to OPTIONALLY use tones. For
instance, if I type "wo" candidates are listed as currently in iBUS, but
the candidate numbers are offset by 5 (to allow tones to be used also). So
the first candidate is numbered 6, etc.
If I then type "wo3", candidates are still numbered from 6, but this time
the candidates are only those with the third inflexion.
Hopefully this feature will be added soon.
Kind Regards,
Matthew
```
Original issue reported on code.google.com by `mister.wardrop` on 2009-10-16 00:29:22
|
1.0
|
Add tone support to default ibus PinYin Engine (like scim) - ```
What version of the product are you using? On what operating system?
OS (Linux distributions, UNIX or ...): Ubuntu GNU/Linux
Architecture (i386, x86_64): i386
IBus version: 1.4.9-1ubuntu2
Input method name and version: iBUS Pinyin 1.3.0
This is a feature request.
The current iBUS pinyin engine is missing something which I really liked
from SCIM; and since everyone seems to be migrating to SCIM these days, I'd
love it if this feature were ported.
In SCIM's pinyin program, it is possible to OPTIONALLY use tones. For
instance, if I type "wo" candidates are listed as currently in iBUS, but
the candidate numbers are offset by 5 (to allow tones to be used also). So
the first candidate is numbered 6, etc.
If I then type "wo3", candidates are still numbered from 6, but this time
the candidates are only those with the third inflexion.
Hopefully this feature will be added soon.
Kind Regards,
Matthew
```
Original issue reported on code.google.com by `mister.wardrop` on 2009-10-16 00:29:22
|
defect
|
add tone support to default ibus pinyin engine like scim what version of the product are you using on what operating system os linux distributions unix or ubuntu gnu linux architecture ibus version input method name and version ibus pinyin this is a feature request the current ibus pinyin engine is missing something which i really liked from scim and since everyone seems to be migrating to scim these days i d love it if this feature were ported in scim s pinyin program it is possible to optionally use tones for instance if i type wo candidates are listed as currently in ibus but the candidate numbers are offset by to allow tones to be used also so the first candidate is numbered etc if i then type candidates are still numbered from but this time the candidates are only those with the third inflexion hopefully this feature will be added soon kind regards matthew original issue reported on code google com by mister wardrop on
| 1
|
13,555
| 2,765,650,804
|
IssuesEvent
|
2015-04-29 21:42:16
|
ljean/modbus-tk
|
https://api.github.com/repos/ljean/modbus-tk
|
closed
|
Device re-connection uses a New Socket and Eventually Fails
|
auto-migrated Priority-Medium Type-Defect
|
```
This is superb implementation and I have been connecting successfully to an
RTU using Modbus TCP/IP over Ipsec for several months.
However the following issue means that the Slave has to be restarted regularly:
1. The connection is over Ipsec and the other end (Cisco, out of my control)
renegotiates the connection every 20 mins
2. When the connection is re-established the Master connects with a new Socket
3. This leads to a 'climb' up the sockets and eventually the Slave freezes.
4. on restart the address is often claimed to be in use
I think there are two issues:
a) using a new socket each time
b) not releasing the address
I suspect b is the socket library but any help on a) or if it is a bug would be
great.
I am using 0.4.2 on Ubuntu 12.04 server, Python 2.7 latest
```
Original issue reported on code.google.com by `nicholas...@gmail.com` on 2 Sep 2013 at 9:30
|
1.0
|
Device re-connection uses a New Socket and Eventually Fails - ```
This is superb implementation and I have been connecting successfully to an
RTU using Modbus TCP/IP over Ipsec for several months.
However the following issue means that the Slave has to be restarted regularly:
1. The connection is over Ipsec and the other end (Cisco, out of my control)
renegotiates the connection every 20 mins
2. When the connection is re-established the Master connects with a new Socket
3. This leads to a 'climb' up the sockets and eventually the Slave freezes.
4. on restart the address is often claimed to be in use
I think there are two issues:
a) using a new socket each time
b) not releasing the address
I suspect b is the socket library but any help on a) or if it is a bug would be
great.
I am using 0.4.2 on Ubuntu 12.04 server, Python 2.7 latest
```
Original issue reported on code.google.com by `nicholas...@gmail.com` on 2 Sep 2013 at 9:30
|
defect
|
device re connection uses a new socket and eventually fails this is superb implementation and i have been connecting successfully to an rtu using modbus tcp ip over ipsec for several months however the following issue means that the slave has to be restarted regularly the connection is over ipsec and the other end cisco out of my control renegotiates the connection every mins when the connection is re established the master connects with a new socket this leads to a climb up the sockets and eventually the slave freezes on restart the address is often claimed to be in use i think there are two issues a using a new socket each time b not releasing the address i suspect b is the socket library but any help on a or if it is a bug would be great i am using on ubuntu server python latest original issue reported on code google com by nicholas gmail com on sep at
| 1
|
42,047
| 10,763,036,035
|
IssuesEvent
|
2019-11-01 02:13:32
|
techo/voluntariado-eventual
|
https://api.github.com/repos/techo/voluntariado-eventual
|
closed
|
Demora envío mail de validación para inscripción en actividad
|
Defecto
|
**Describí el error**
Al querer inscribirse en una actividad, se pide validar el mail previamente a seguir el proceso de inscripción. Este mail se envía con demoras de 2 días a 1 semana, atrasando el proceso de inscripción y hasta a veces, impidiendo el mismo si no se tiene conocimiento del caso.
**Para reproducirlo**
Pasos para reproducir el comportamiento:
1. Ir a la actividad en cuestión e inscribirse
2. Clickear en Inscribirme
3. Para continuar te pide primero, entres a tu correo y valides el mail enviado.
**Comportamiento esperando**
Que el mail de de validación de correo, para continuar con la inscripción sea inmediato.
**Contexto adicional**
Ejemplos de correo en la fecha que se pidió validación y en la fecha donde recibieron el correo:
facundostyles94@gmail.com solicito validación el viernes 11 de Octubre y recibió el mail el viernes 18 de Octubre
luislopestecho@gmail.com
Miércoles 16 de Octubre solicito validación de mail y sigue sin recibir mail de validación
solgeminiani14@gmail.com Miércoles 16 de Octubre solicito la validación de Mail y el 18 recibió el mail correspondiente al correo.
|
1.0
|
Demora envío mail de validación para inscripción en actividad - **Describí el error**
Al querer inscribirse en una actividad, se pide validar el mail previamente a seguir el proceso de inscripción. Este mail se envía con demoras de 2 días a 1 semana, atrasando el proceso de inscripción y hasta a veces, impidiendo el mismo si no se tiene conocimiento del caso.
**Para reproducirlo**
Pasos para reproducir el comportamiento:
1. Ir a la actividad en cuestión e inscribirse
2. Clickear en Inscribirme
3. Para continuar te pide primero, entres a tu correo y valides el mail enviado.
**Comportamiento esperando**
Que el mail de de validación de correo, para continuar con la inscripción sea inmediato.
**Contexto adicional**
Ejemplos de correo en la fecha que se pidió validación y en la fecha donde recibieron el correo:
facundostyles94@gmail.com solicito validación el viernes 11 de Octubre y recibió el mail el viernes 18 de Octubre
luislopestecho@gmail.com
Miércoles 16 de Octubre solicito validación de mail y sigue sin recibir mail de validación
solgeminiani14@gmail.com Miércoles 16 de Octubre solicito la validación de Mail y el 18 recibió el mail correspondiente al correo.
|
defect
|
demora envío mail de validación para inscripción en actividad describí el error al querer inscribirse en una actividad se pide validar el mail previamente a seguir el proceso de inscripción este mail se envía con demoras de días a semana atrasando el proceso de inscripción y hasta a veces impidiendo el mismo si no se tiene conocimiento del caso para reproducirlo pasos para reproducir el comportamiento ir a la actividad en cuestión e inscribirse clickear en inscribirme para continuar te pide primero entres a tu correo y valides el mail enviado comportamiento esperando que el mail de de validación de correo para continuar con la inscripción sea inmediato contexto adicional ejemplos de correo en la fecha que se pidió validación y en la fecha donde recibieron el correo gmail com solicito validación el viernes de octubre y recibió el mail el viernes de octubre luislopestecho gmail com miércoles de octubre solicito validación de mail y sigue sin recibir mail de validación gmail com miércoles de octubre solicito la validación de mail y el recibió el mail correspondiente al correo
| 1
|
134,241
| 18,452,752,084
|
IssuesEvent
|
2021-10-15 12:57:12
|
bgoonz/BGOONZ_BLOG_2.0
|
https://api.github.com/repos/bgoonz/BGOONZ_BLOG_2.0
|
opened
|
CVE-2020-28469 (High) detected in glob-parent-3.1.0.tgz
|
security vulnerability
|
## CVE-2020-28469 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>glob-parent-3.1.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>Path to dependency file: BGOONZ_BLOG_2.0/package.json</p>
<p>Path to vulnerable library: BGOONZ_BLOG_2.0/node_modules/watchpack-chokidar2/node_modules/glob-parent/package.json,BGOONZ_BLOG_2.0/node_modules/webpack-dev-server/node_modules/glob-parent/package.json,BGOONZ_BLOG_2.0/node_modules/glob-stream/node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- gatsby-2.32.8.tgz (Root Library)
- webpack-4.46.0.tgz
- watchpack-1.7.5.tgz
- watchpack-chokidar2-2.0.1.tgz
- chokidar-2.1.8.tgz
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/bgoonz/BGOONZ_BLOG_2.0/commit/4ac284617e126250a26acd6d15bf7f6ee55620be">4ac284617e126250a26acd6d15bf7f6ee55620be</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution: glob-parent - 5.1.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2020-28469 (High) detected in glob-parent-3.1.0.tgz - ## CVE-2020-28469 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>glob-parent-3.1.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>Path to dependency file: BGOONZ_BLOG_2.0/package.json</p>
<p>Path to vulnerable library: BGOONZ_BLOG_2.0/node_modules/watchpack-chokidar2/node_modules/glob-parent/package.json,BGOONZ_BLOG_2.0/node_modules/webpack-dev-server/node_modules/glob-parent/package.json,BGOONZ_BLOG_2.0/node_modules/glob-stream/node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- gatsby-2.32.8.tgz (Root Library)
- webpack-4.46.0.tgz
- watchpack-1.7.5.tgz
- watchpack-chokidar2-2.0.1.tgz
- chokidar-2.1.8.tgz
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/bgoonz/BGOONZ_BLOG_2.0/commit/4ac284617e126250a26acd6d15bf7f6ee55620be">4ac284617e126250a26acd6d15bf7f6ee55620be</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution: glob-parent - 5.1.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve high detected in glob parent tgz cve high severity vulnerability vulnerable library glob parent tgz strips glob magic from a string to provide the parent directory path library home page a href path to dependency file bgoonz blog package json path to vulnerable library bgoonz blog node modules watchpack node modules glob parent package json bgoonz blog node modules webpack dev server node modules glob parent package json bgoonz blog node modules glob stream node modules glob parent package json dependency hierarchy gatsby tgz root library webpack tgz watchpack tgz watchpack tgz chokidar tgz x glob parent tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package glob parent before the enclosure regex used to check for strings ending in enclosure containing path separator publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution glob parent step up your open source security game with whitesource
| 0
|
731,799
| 25,231,429,503
|
IssuesEvent
|
2022-11-14 20:11:13
|
YunoHost/issues
|
https://api.github.com/repos/YunoHost/issues
|
closed
|
A reply email may contain unwanted meta data about default domain (in Delivered-To field)
|
:space_invader: bug :mailbox: Email Priority: low
|
###### Original Redmine Issue: [964](https://dev.yunohost.org/issues/964)
Author Name: **fr0g**
---
**Given**
Two yunohost domains A and B, with A being the default domain.
Yunohost user "user" with email "bob@B"
**Test Case**
Some user alice@X sends email reply to bob@B, where X is some server outside the configured yunohost environment.
**Expectation**
There should be no data about domain A and/or the yunohost login user for "bob@B" in the email headers which would be leaked with a forward of or reply to this email.
**Current behaviour**
The following data about A in the email headers:
1. Delivered-To: user@A, where user is the yunohost login for bob@B
|
1.0
|
A reply email may contain unwanted meta data about default domain (in Delivered-To field) - ###### Original Redmine Issue: [964](https://dev.yunohost.org/issues/964)
Author Name: **fr0g**
---
**Given**
Two yunohost domains A and B, with A being the default domain.
Yunohost user "user" with email "bob@B"
**Test Case**
Some user alice@X sends email reply to bob@B, where X is some server outside the configured yunohost environment.
**Expectation**
There should be no data about domain A and/or the yunohost login user for "bob@B" in the email headers which would be leaked with a forward of or reply to this email.
**Current behaviour**
The following data about A in the email headers:
1. Delivered-To: user@A, where user is the yunohost login for bob@B
|
non_defect
|
a reply email may contain unwanted meta data about default domain in delivered to field original redmine issue author name given two yunohost domains a and b with a being the default domain yunohost user user with email bob b test case some user alice x sends email reply to bob b where x is some server outside the configured yunohost environment expectation there should be no data about domain a and or the yunohost login user for bob b in the email headers which would be leaked with a forward of or reply to this email current behaviour the following data about a in the email headers delivered to user a where user is the yunohost login for bob b
| 0
|
255,656
| 27,488,748,616
|
IssuesEvent
|
2023-03-04 10:59:47
|
SoggySocks2/SampleApp
|
https://api.github.com/repos/SoggySocks2/SampleApp
|
opened
|
jquery.validate-1.17.0.js: 1 vulnerabilities (highest severity is: 7.5)
|
security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery.validate-1.17.0.js</b></p></summary>
<p>Client-side form validation made easy</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery-validate/1.17.0/jquery.validate.js">https://cdnjs.cloudflare.com/ajax/libs/jquery-validate/1.17.0/jquery.validate.js</a></p>
<p>Path to vulnerable library: /SampleApp.WebUI/wwwroot/lib/jquery-validation/dist/jquery.validate.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/SoggySocks2/SampleApp/commit/1725e2b1e54afe5d02396de7287a49b2f0bc9a44">1725e2b1e54afe5d02396de7287a49b2f0bc9a44</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (jquery.validate version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-21252](https://www.mend.io/vulnerability-database/CVE-2021-21252) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | jquery.validate-1.17.0.js | Direct | jquery-validation - 1.19.3 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-21252</summary>
### Vulnerable Library - <b>jquery.validate-1.17.0.js</b></p>
<p>Client-side form validation made easy</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery-validate/1.17.0/jquery.validate.js">https://cdnjs.cloudflare.com/ajax/libs/jquery-validate/1.17.0/jquery.validate.js</a></p>
<p>Path to vulnerable library: /SampleApp.WebUI/wwwroot/lib/jquery-validation/dist/jquery.validate.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery.validate-1.17.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/SoggySocks2/SampleApp/commit/1725e2b1e54afe5d02396de7287a49b2f0bc9a44">1725e2b1e54afe5d02396de7287a49b2f0bc9a44</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The jQuery Validation Plugin provides drop-in validation for your existing forms. It is published as an npm package "jquery-validation". jquery-validation before version 1.19.3 contains one or more regular expressions that are vulnerable to ReDoS (Regular Expression Denial of Service). This is fixed in 1.19.3.
<p>Publish Date: 2021-01-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-21252>CVE-2021-21252</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jxwx-85vp-gvwm">https://github.com/advisories/GHSA-jxwx-85vp-gvwm</a></p>
<p>Release Date: 2021-01-13</p>
<p>Fix Resolution: jquery-validation - 1.19.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
|
True
|
jquery.validate-1.17.0.js: 1 vulnerabilities (highest severity is: 7.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery.validate-1.17.0.js</b></p></summary>
<p>Client-side form validation made easy</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery-validate/1.17.0/jquery.validate.js">https://cdnjs.cloudflare.com/ajax/libs/jquery-validate/1.17.0/jquery.validate.js</a></p>
<p>Path to vulnerable library: /SampleApp.WebUI/wwwroot/lib/jquery-validation/dist/jquery.validate.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/SoggySocks2/SampleApp/commit/1725e2b1e54afe5d02396de7287a49b2f0bc9a44">1725e2b1e54afe5d02396de7287a49b2f0bc9a44</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (jquery.validate version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-21252](https://www.mend.io/vulnerability-database/CVE-2021-21252) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | jquery.validate-1.17.0.js | Direct | jquery-validation - 1.19.3 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-21252</summary>
### Vulnerable Library - <b>jquery.validate-1.17.0.js</b></p>
<p>Client-side form validation made easy</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery-validate/1.17.0/jquery.validate.js">https://cdnjs.cloudflare.com/ajax/libs/jquery-validate/1.17.0/jquery.validate.js</a></p>
<p>Path to vulnerable library: /SampleApp.WebUI/wwwroot/lib/jquery-validation/dist/jquery.validate.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery.validate-1.17.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/SoggySocks2/SampleApp/commit/1725e2b1e54afe5d02396de7287a49b2f0bc9a44">1725e2b1e54afe5d02396de7287a49b2f0bc9a44</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The jQuery Validation Plugin provides drop-in validation for your existing forms. It is published as an npm package "jquery-validation". jquery-validation before version 1.19.3 contains one or more regular expressions that are vulnerable to ReDoS (Regular Expression Denial of Service). This is fixed in 1.19.3.
<p>Publish Date: 2021-01-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-21252>CVE-2021-21252</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jxwx-85vp-gvwm">https://github.com/advisories/GHSA-jxwx-85vp-gvwm</a></p>
<p>Release Date: 2021-01-13</p>
<p>Fix Resolution: jquery-validation - 1.19.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
|
non_defect
|
jquery validate js vulnerabilities highest severity is vulnerable library jquery validate js client side form validation made easy library home page a href path to vulnerable library sampleapp webui wwwroot lib jquery validation dist jquery validate js found in head commit a href vulnerabilities cve severity cvss dependency type fixed in jquery validate version remediation available high jquery validate js direct jquery validation details cve vulnerable library jquery validate js client side form validation made easy library home page a href path to vulnerable library sampleapp webui wwwroot lib jquery validation dist jquery validate js dependency hierarchy x jquery validate js vulnerable library found in head commit a href found in base branch master vulnerability details the jquery validation plugin provides drop in validation for your existing forms it is published as an npm package jquery validation jquery validation before version contains one or more regular expressions that are vulnerable to redos regular expression denial of service this is fixed in publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery validation step up your open source security game with mend
| 0
|
99,160
| 8,691,325,748
|
IssuesEvent
|
2018-12-04 00:50:12
|
Microsoft/ptvsd
|
https://api.github.com/repos/Microsoft/ptvsd
|
closed
|
Test does not kill all processes
|
bug test issue
|
## Environment data
- PTVSD version: master
- OS and version: Any
- Python version (& distribution if applicable, e.g. Anaconda): Any
- Using VS Code or Visual Studio: console
## Actual behavior
After running full set of tests, often there are python test instances left behind.
## Expected behavior
Test should kill all processes launched as a part of the test.
## Steps to reproduce:
Run all tests under [pytests](pytests) a bunch of times
|
1.0
|
Test does not kill all processes - ## Environment data
- PTVSD version: master
- OS and version: Any
- Python version (& distribution if applicable, e.g. Anaconda): Any
- Using VS Code or Visual Studio: console
## Actual behavior
After running full set of tests, often there are python test instances left behind.
## Expected behavior
Test should kill all processes launched as a part of the test.
## Steps to reproduce:
Run all tests under [pytests](pytests) a bunch of times
|
non_defect
|
test does not kill all processes environment data ptvsd version master os and version any python version distribution if applicable e g anaconda any using vs code or visual studio console actual behavior after running full set of tests often there are python test instances left behind expected behavior test should kill all processes launched as a part of the test steps to reproduce run all tests under pytests a bunch of times
| 0
|
12,748
| 2,715,362,945
|
IssuesEvent
|
2015-04-10 12:37:57
|
laurentpetit/ccw
|
https://api.github.com/repos/laurentpetit/ccw
|
closed
|
Key for switching between clojure editor modes not described in Help.
|
defect Priority-Critical
|
Original [issue 305](https://code.google.com/p/counterclockwise/issues/detail?id=305) created by laurentpetit on 2011-11-28T09:14:32.000Z:
The Alt-D key combo for switching editor modes is not mentioned in the Help text. The only place I could find it is in the Clojure menu.
|
1.0
|
Key for switching between clojure editor modes not described in Help. - Original [issue 305](https://code.google.com/p/counterclockwise/issues/detail?id=305) created by laurentpetit on 2011-11-28T09:14:32.000Z:
The Alt-D key combo for switching editor modes is not mentioned in the Help text. The only place I could find it is in the Clojure menu.
|
defect
|
key for switching between clojure editor modes not described in help original created by laurentpetit on the alt d key combo for switching editor modes is not mentioned in the help text the only place i could find it is in the clojure menu
| 1
|
99,921
| 21,075,618,499
|
IssuesEvent
|
2022-04-02 04:55:52
|
llvm/llvm-project
|
https://api.github.com/repos/llvm/llvm-project
|
closed
|
-Wdeclaration-after-statement in arm_neon.h
|
clang:codegen release:backport
|
The Linux kernel is looking to [upgrade from `-std=gnu89` to `-std=gnu11`](https://lore.kernel.org/r/CAHk-=wh97QY9fEQUK6zMVQwaQ_JWDvR=R+TxQ_0OYrMHQ+egvQ@mail.gmail.com/). The kernel builds with `-Wdeclaration-after-statement`, which exposes an issue in `arm_neon.h` with arm64 big endian: https://godbolt.org/z/313sW6zrW
```
$ cat repro.c
#include <arm_neon.h>
static inline uint8x16_t SHLBYTE(uint8x16_t v)
{
return vshlq_n_u8(v, 1);
}
$ clang --target=aarch64-linux-gnu -mbig-endian -std=gnu11 -Wdeclaration-after-statement -fsyntax-only -ffreestanding repro.c
repro.c:5:9: warning: mixing declarations and code is incompatible with standards before C99 [-Wdeclaration-after-statement]
return vshlq_n_u8(v, 1);
^
.../lib/clang/15.0.0/include/arm_neon.h:24823:14: note: expanded from macro 'vshlq_n_u8'
uint8x16_t __ret; \
^
1 warning generated.
$ clang --target=aarch64-linux-gnu -mbig-endian -std=gnu89 -Wdeclaration-after-statement -fsyntax-only repro.c
```
As far as I understand based on reading `clang::ProcessWarningOptions()` and `DiagnosticIDs::getDiagnosticSeverity()`, there should not be any warnings from system headers if `-Wsystem-headers` is not passed, which the kernel does not do.
|
1.0
|
-Wdeclaration-after-statement in arm_neon.h - The Linux kernel is looking to [upgrade from `-std=gnu89` to `-std=gnu11`](https://lore.kernel.org/r/CAHk-=wh97QY9fEQUK6zMVQwaQ_JWDvR=R+TxQ_0OYrMHQ+egvQ@mail.gmail.com/). The kernel builds with `-Wdeclaration-after-statement`, which exposes an issue in `arm_neon.h` with arm64 big endian: https://godbolt.org/z/313sW6zrW
```
$ cat repro.c
#include <arm_neon.h>
static inline uint8x16_t SHLBYTE(uint8x16_t v)
{
return vshlq_n_u8(v, 1);
}
$ clang --target=aarch64-linux-gnu -mbig-endian -std=gnu11 -Wdeclaration-after-statement -fsyntax-only -ffreestanding repro.c
repro.c:5:9: warning: mixing declarations and code is incompatible with standards before C99 [-Wdeclaration-after-statement]
return vshlq_n_u8(v, 1);
^
.../lib/clang/15.0.0/include/arm_neon.h:24823:14: note: expanded from macro 'vshlq_n_u8'
uint8x16_t __ret; \
^
1 warning generated.
$ clang --target=aarch64-linux-gnu -mbig-endian -std=gnu89 -Wdeclaration-after-statement -fsyntax-only repro.c
```
As far as I understand based on reading `clang::ProcessWarningOptions()` and `DiagnosticIDs::getDiagnosticSeverity()`, there should not be any warnings from system headers if `-Wsystem-headers` is not passed, which the kernel does not do.
|
non_defect
|
wdeclaration after statement in arm neon h the linux kernel is looking to the kernel builds with wdeclaration after statement which exposes an issue in arm neon h with big endian cat repro c include static inline t shlbyte t v return vshlq n v clang target linux gnu mbig endian std wdeclaration after statement fsyntax only ffreestanding repro c repro c warning mixing declarations and code is incompatible with standards before return vshlq n v lib clang include arm neon h note expanded from macro vshlq n t ret warning generated clang target linux gnu mbig endian std wdeclaration after statement fsyntax only repro c as far as i understand based on reading clang processwarningoptions and diagnosticids getdiagnosticseverity there should not be any warnings from system headers if wsystem headers is not passed which the kernel does not do
| 0
|
40,774
| 10,153,401,599
|
IssuesEvent
|
2019-08-06 04:22:00
|
bridgedotnet/Bridge
|
https://api.github.com/repos/bridgedotnet/Bridge
|
closed
|
Lost kind of DateTime for Date property
|
defect
|
Probably it can be regression (I cannot check).
### Steps To Reproduce
https://deck.net/6f0314132592c64c13b048f2b8d8ef47
```csharp
internal class Program
{
private static void Main(string[] args)
{
DateTime date1 = DateTime.SpecifyKind(DateTime.Today, DateTimeKind.Utc);
Console.WriteLine(date1.Kind.ToString());
DateTime date2 = date1.Date;
Console.WriteLine(date2.Kind.ToString());
}
}
```
### Expected Result
```
Utc
Utc
```
### Actual Result
```
Utc
Unspecified
```
|
1.0
|
Lost kind of DateTime for Date property - Probably it can be regression (I cannot check).
### Steps To Reproduce
https://deck.net/6f0314132592c64c13b048f2b8d8ef47
```csharp
internal class Program
{
private static void Main(string[] args)
{
DateTime date1 = DateTime.SpecifyKind(DateTime.Today, DateTimeKind.Utc);
Console.WriteLine(date1.Kind.ToString());
DateTime date2 = date1.Date;
Console.WriteLine(date2.Kind.ToString());
}
}
```
### Expected Result
```
Utc
Utc
```
### Actual Result
```
Utc
Unspecified
```
|
defect
|
lost kind of datetime for date property probably it can be regression i cannot check steps to reproduce csharp internal class program private static void main string args datetime datetime specifykind datetime today datetimekind utc console writeline kind tostring datetime date console writeline kind tostring expected result utc utc actual result utc unspecified
| 1
|
196,650
| 6,937,039,063
|
IssuesEvent
|
2017-12-04 01:55:49
|
webcompat/web-bugs
|
https://api.github.com/repos/webcompat/web-bugs
|
closed
|
m.facebook.com - design is broken
|
browser-firefox-mobile priority-critical status-needsinfo
|
<!-- @browser: Firefox Mobile 59.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 6.0.1; Mobile; rv:59.0) Gecko/59.0 Firefox/59.0 -->
<!-- @reported_with: web -->
**URL**: https://m.facebook.com/?_rdr#~!/?soft=notifications
**Browser / Version**: Firefox Mobile 59.0
**Operating System**: Android 6.0.1
**Tested Another Browser**: No
**Problem type**: Design is broken
**Description**: it was seen as half desktop's size
**Steps to Reproduce**:
No matter I didn't click it .. and then clicked desktop size in order to send report only
_From [webcompat.com](https://webcompat.com/) with ❤️_
|
1.0
|
m.facebook.com - design is broken - <!-- @browser: Firefox Mobile 59.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 6.0.1; Mobile; rv:59.0) Gecko/59.0 Firefox/59.0 -->
<!-- @reported_with: web -->
**URL**: https://m.facebook.com/?_rdr#~!/?soft=notifications
**Browser / Version**: Firefox Mobile 59.0
**Operating System**: Android 6.0.1
**Tested Another Browser**: No
**Problem type**: Design is broken
**Description**: it was seen as half desktop's size
**Steps to Reproduce**:
No matter I didn't click it .. and then clicked desktop size in order to send report only
_From [webcompat.com](https://webcompat.com/) with ❤️_
|
non_defect
|
m facebook com design is broken url browser version firefox mobile operating system android tested another browser no problem type design is broken description it was seen as half desktop s size steps to reproduce no matter i didn t click it and then clicked desktop size in order to send report only from with ❤️
| 0
|
12,174
| 3,052,181,505
|
IssuesEvent
|
2015-08-12 13:29:52
|
mesosphere/marathon
|
https://api.github.com/repos/mesosphere/marathon
|
closed
|
Expose task failures in the UI
|
design enhancement gui Size: M
|
We store task failures in the `TaskFailureRepository`, but don't make them visible in the UI. This should be fixed. To retrieve failures from the `/v2/apps` endpoint, it should be called with `?embed=apps.failures`.
|
1.0
|
Expose task failures in the UI - We store task failures in the `TaskFailureRepository`, but don't make them visible in the UI. This should be fixed. To retrieve failures from the `/v2/apps` endpoint, it should be called with `?embed=apps.failures`.
|
non_defect
|
expose task failures in the ui we store task failures in the taskfailurerepository but don t make them visible in the ui this should be fixed to retrieve failures from the apps endpoint it should be called with embed apps failures
| 0
|
238,982
| 26,196,912,164
|
IssuesEvent
|
2023-01-03 14:15:43
|
Nehamaefi/Efigit
|
https://api.github.com/repos/Nehamaefi/Efigit
|
opened
|
CVE-2022-1471 (High) detected in snakeyaml-1.6.jar
|
security vulnerability
|
## CVE-2022-1471 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snakeyaml-1.6.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://code.google.com/p/snakeyaml/">http://code.google.com/p/snakeyaml/</a></p>
<p>Path to dependency file: /core/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/org/yaml/snakeyaml/1.6/snakeyaml-1.6.jar</p>
<p>
Dependency Hierarchy:
- testng-5.14.10.jar (Root Library)
- :x: **snakeyaml-1.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Nehamaefi/Efigit/commit/3071fd0d33f44f6dd9964fbdb4688b60b1adebbc">3071fd0d33f44f6dd9964fbdb4688b60b1adebbc</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
SnakeYaml's Constructor() class does not restrict types which can be instantiated during deserialization. Deserializing yaml content provided by an attacker can lead to remote code execution. We recommend using SnakeYaml's SafeConsturctor when parsing untrusted content to restrict deserialization.
<p>Publish Date: 2022-12-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-1471>CVE-2022-1471</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
|
True
|
CVE-2022-1471 (High) detected in snakeyaml-1.6.jar - ## CVE-2022-1471 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snakeyaml-1.6.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://code.google.com/p/snakeyaml/">http://code.google.com/p/snakeyaml/</a></p>
<p>Path to dependency file: /core/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/org/yaml/snakeyaml/1.6/snakeyaml-1.6.jar</p>
<p>
Dependency Hierarchy:
- testng-5.14.10.jar (Root Library)
- :x: **snakeyaml-1.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Nehamaefi/Efigit/commit/3071fd0d33f44f6dd9964fbdb4688b60b1adebbc">3071fd0d33f44f6dd9964fbdb4688b60b1adebbc</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
SnakeYaml's Constructor() class does not restrict types which can be instantiated during deserialization. Deserializing yaml content provided by an attacker can lead to remote code execution. We recommend using SnakeYaml's SafeConsturctor when parsing untrusted content to restrict deserialization.
<p>Publish Date: 2022-12-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-1471>CVE-2022-1471</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
|
non_defect
|
cve high detected in snakeyaml jar cve high severity vulnerability vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file core pom xml path to vulnerable library root repository org yaml snakeyaml snakeyaml jar dependency hierarchy testng jar root library x snakeyaml jar vulnerable library found in head commit a href found in base branch master vulnerability details snakeyaml s constructor class does not restrict types which can be instantiated during deserialization deserializing yaml content provided by an attacker can lead to remote code execution we recommend using snakeyaml s safeconsturctor when parsing untrusted content to restrict deserialization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href
| 0
|
30,963
| 6,378,705,293
|
IssuesEvent
|
2017-08-02 13:20:17
|
sous-chefs/ruby_rbenv
|
https://api.github.com/repos/sous-chefs/ruby_rbenv
|
closed
|
user_installs not installing rbenv, just rbenv-install
|
Defect Pending Feedback
|
### Cookbook version
* 1.2.0
### Chef-client version
* 13.1.31
### Platform Details
1. OSX 10.12.5 running Docker CE Version 17.03.1-ce-mac12 (17661)
2. $ chef -v
```
Chef Development Kit Version: 1.3.43
chef-client version: 12.19.36
delivery version: master (dd319aa632c2f550c92a2172b9d1226478fea997)
berks version: 5.6.4
kitchen version: 1.16.0
```
### Scenario:
Install rbenv, and a ruby for a specific user
### Steps to Reproduce:
* [Following what I believe should be the correct way to do this](https://github.com/sous-chefs/ruby_rbenv#-rbenv-installed-for-a-specific-user-with-rubies)
`include_recipe 'rbenv_ruby::user_install'` in a recipe and populate the `node.default['rbenv']['user_installs']` with the example information, but using Ruby 2.4.1. Also including the recipes in the run list for kitchen yielded the same result.
cookbook excerpt:
```
node.override['rbenv']['user_installs'] = [
{ 'user' => 'lita',
'rubies' => ['2.4.1'],
'global' => '2.4.1',
'gems' => {
'2.4.1' => [
{ 'name' => 'bundler' },
{ 'name' => 'rake' },
{ 'name' => 'thor' },
{ 'name' => 'lita' }
]
}
}
]
node.override['rbenv']['rubies'] = [ '2.4.1' ]
include_recipe 'ruby_rbenv::user'
include_recipe 'ruby_build'
```
### Expected Result:
either rbenv should be installed, or rbenv with ruby-build plugin should be installed, or a version of ruby after compiling, which should take a significant amount of time.
### Actual Result:
Actual results below. For some reason the only available commands relating to rbenv are `rbenv-install` and `rbenv-uninstall`, but no actual `rbenv`.
```
Thank you for installing Chef!
Transferring files to <default-centos-73>
Starting Chef Client, version 13.1.31
[2017-06-24T04:17:31+00:00] WARN: Plugin Network: unable to detect ipaddress
[2017-06-24T04:17:31+00:00] WARN: Plugin Network: unable to detect ipaddress
Creating a new client identity for default-centos-73 using the validator key.
resolving cookbooks for run list: ["wheatley_cookbook::default"]
Synchronizing Cookbooks:
- wheatley_cookbook (0.1.0)
- redisio (2.6.1)
- ruby_build (1.1.0)
- ruby_rbenv (1.2.1)
- build-essential (8.0.3)
- ulimit (0.4.0)
- selinux_policy (2.0.1)
- yum-epel (2.1.2)
- seven_zip (2.0.2)
- git (6.1.0)
- mingw (2.0.1)
- compat_resource (12.19.0)
- dmg (4.0.0)
- ohai (5.1.0)
- windows (3.1.1)
Installing Cookbook Gems:
Compiling Cookbooks...
Converging 12 resources
Recipe: wheatley_cookbook::user_setup
* group[lita] action create
- create group lita
* linux_user[lita] action create
- create user lita
* directory[/home/lita] action create
- create new directory /home/lita
- change owner from '' to 'lita'
- change group from '' to 'lita'
Recipe: ruby_rbenv::user_install
* yum_package[git] action install
- install version 1.8.3.1-6.el7_2.1 of package git
* yum_package[grep] action install (up to date)
* template[/etc/profile.d/rbenv.sh] action create
- create new file /etc/profile.d/rbenv.sh
- update content in file /etc/profile.d/rbenv.sh from none to efa757
--- /etc/profile.d/rbenv.sh 2017-06-24 04:17:54.556691091 +0000
+++ /etc/profile.d/.chef-rbenv20170624-171-12a6oy5.sh 2017-06-24 04:17:54.546702168 +0000
@@ -1 +1,16 @@
+# Generated by Chef for 0804fd1c4919
+# Local modifications will be overridden
+
+# prefer a user rbenv over a system wide install
+if [ -s "${HOME}/.rbenv/bin" ]; then
+ rbenv_root="${HOME}/.rbenv"
+elif [ -s "/usr/local/rbenv" ]; then
+ rbenv_root="/usr/local/rbenv"
+ export RBENV_ROOT="$rbenv_root"
+fi
+
+if [ -n "$rbenv_root" ]; then
+ export PATH="${rbenv_root}/bin:$PATH"
+ eval "$(rbenv init -)"
+fi
- change mode from '' to '0755'
- change owner from '' to 'root'
Recipe: yum-epel::default
* yum_repository[epel] action create
* template[/etc/yum.repos.d/epel.repo] action create
- create new file /etc/yum.repos.d/epel.repo
- update content in file /etc/yum.repos.d/epel.repo from none to c7a666
--- /etc/yum.repos.d/epel.repo 2017-06-24 04:17:54.566680014 +0000
+++ /etc/yum.repos.d/.chef-epel20170624-171-vg208y.repo 2017-06-24 04:17:54.566680014 +0000
@@ -1 +1,12 @@
+# This file was generated by Chef
+# Do NOT modify this file by hand.
+
+[epel]
+name=Extra Packages for 7 - $basearch
+enabled=1
+failovermethod=priority
+fastestmirror_enabled=0
+gpgcheck=1
+gpgkey=https://download.fedoraproject.org/pub/epel/RPM-GPG-KEY-EPEL-7
+mirrorlist=http://mirrors.fedoraproject.org/mirrorlist?repo=epel-7&arch=$basearch
- change mode from '' to '0644'
* execute[yum clean metadata epel] action run
- execute yum clean metadata --disablerepo=* --enablerepo=epel
* execute[yum-makecache-epel] action run
- execute yum -q -y makecache --disablerepo=* --enablerepo=epel
* ruby_block[yum-cache-reload-epel] action create
- execute the ruby block yum-cache-reload-epel
* execute[yum clean metadata epel] action nothing (skipped due to action :nothing)
* execute[yum-makecache-epel] action nothing (skipped due to action :nothing)
* ruby_block[yum-cache-reload-epel] action nothing (skipped due to action :nothing)
Recipe: git::package
* git_client[default] action install
* yum_package[default :create git] action install (up to date)
(up to date)
Recipe: ruby_build::default
* yum_package[tar, bash, curl] action install (up to date)
* execute[Install ruby-build] action nothing (skipped due to action :nothing)
* directory[/tmp/kitchen/cache] action create (up to date)
* git[/tmp/kitchen/cache/ruby-build] action checkout
- clone from https://github.com/rbenv/ruby-build.git into /tmp/kitchen/cache/ruby-build
- checkout ref 476d09b66a14392989c3c65793428742e1d9f951 branch master
* execute[Install ruby-build] action run
- execute ./install.sh
Running handlers:
Running handlers complete
Chef Client finished, 12/21 resources updated in 36 seconds
Finished converging <default-centos-73> (0m57.52s).
-----> Setting up <default-centos-73>...
Finished setting up <default-centos-73> (0m0.00s).
-----> Verifying <default-centos-73>...
Loaded tests from test/smoke/default
Profile: tests from test/smoke/default
Version: (not specified)
Target: ssh://kitchen@localhost:32777
File /home/lita/.rbenv/bin/rbenv
∅ should exist
expected File /home/lita/.rbenv/bin/rbenv to exist
Group lita
✔ should exist
User lita
✔ should exist
✔ group should eq "lita"
✔ home should eq "/home/lita"
✔ shell should eq "/bin/bash"
File /home/lita
✔ should exist
✔ owner should eq "lita"
✔ group should eq "lita"
Test Summary: 8 successful, 1 failures, 0 skipped
>>>>>> ------Exception-------
>>>>>> Class: Kitchen::ActionFailed
>>>>>> Message: 1 actions failed.
>>>>>> Verify failed on instance <default-centos-73>. Please see .kitchen/logs/default-centos-73.log for more details
>>>>>> ----------------------
>>>>>> Please see .kitchen/logs/kitchen.log for more details
>>>>>> Also try running `kitchen diagnose --all` for configuration
```
|
1.0
|
user_installs not installing rbenv, just rbenv-install - ### Cookbook version
* 1.2.0
### Chef-client version
* 13.1.31
### Platform Details
1. OSX 10.12.5 running Docker CE Version 17.03.1-ce-mac12 (17661)
2. $ chef -v
```
Chef Development Kit Version: 1.3.43
chef-client version: 12.19.36
delivery version: master (dd319aa632c2f550c92a2172b9d1226478fea997)
berks version: 5.6.4
kitchen version: 1.16.0
```
### Scenario:
Install rbenv, and a ruby for a specific user
### Steps to Reproduce:
* [Following what I believe should be the correct way to do this](https://github.com/sous-chefs/ruby_rbenv#-rbenv-installed-for-a-specific-user-with-rubies)
`include_recipe 'rbenv_ruby::user_install'` in a recipe and populate the `node.default['rbenv']['user_installs']` with the example information, but using Ruby 2.4.1. Also including the recipes in the run list for kitchen yielded the same result.
cookbook excerpt:
```
node.override['rbenv']['user_installs'] = [
{ 'user' => 'lita',
'rubies' => ['2.4.1'],
'global' => '2.4.1',
'gems' => {
'2.4.1' => [
{ 'name' => 'bundler' },
{ 'name' => 'rake' },
{ 'name' => 'thor' },
{ 'name' => 'lita' }
]
}
}
]
node.override['rbenv']['rubies'] = [ '2.4.1' ]
include_recipe 'ruby_rbenv::user'
include_recipe 'ruby_build'
```
### Expected Result:
either rbenv should be installed, or rbenv with ruby-build plugin should be installed, or a version of ruby after compiling, which should take a significant amount of time.
### Actual Result:
Actual results below. For some reason the only available commands relating to rbenv are `rbenv-install` and `rbenv-uninstall`, but no actual `rbenv`.
```
Thank you for installing Chef!
Transferring files to <default-centos-73>
Starting Chef Client, version 13.1.31
[2017-06-24T04:17:31+00:00] WARN: Plugin Network: unable to detect ipaddress
[2017-06-24T04:17:31+00:00] WARN: Plugin Network: unable to detect ipaddress
Creating a new client identity for default-centos-73 using the validator key.
resolving cookbooks for run list: ["wheatley_cookbook::default"]
Synchronizing Cookbooks:
- wheatley_cookbook (0.1.0)
- redisio (2.6.1)
- ruby_build (1.1.0)
- ruby_rbenv (1.2.1)
- build-essential (8.0.3)
- ulimit (0.4.0)
- selinux_policy (2.0.1)
- yum-epel (2.1.2)
- seven_zip (2.0.2)
- git (6.1.0)
- mingw (2.0.1)
- compat_resource (12.19.0)
- dmg (4.0.0)
- ohai (5.1.0)
- windows (3.1.1)
Installing Cookbook Gems:
Compiling Cookbooks...
Converging 12 resources
Recipe: wheatley_cookbook::user_setup
* group[lita] action create
- create group lita
* linux_user[lita] action create
- create user lita
* directory[/home/lita] action create
- create new directory /home/lita
- change owner from '' to 'lita'
- change group from '' to 'lita'
Recipe: ruby_rbenv::user_install
* yum_package[git] action install
- install version 1.8.3.1-6.el7_2.1 of package git
* yum_package[grep] action install (up to date)
* template[/etc/profile.d/rbenv.sh] action create
- create new file /etc/profile.d/rbenv.sh
- update content in file /etc/profile.d/rbenv.sh from none to efa757
--- /etc/profile.d/rbenv.sh 2017-06-24 04:17:54.556691091 +0000
+++ /etc/profile.d/.chef-rbenv20170624-171-12a6oy5.sh 2017-06-24 04:17:54.546702168 +0000
@@ -1 +1,16 @@
+# Generated by Chef for 0804fd1c4919
+# Local modifications will be overridden
+
+# prefer a user rbenv over a system wide install
+if [ -s "${HOME}/.rbenv/bin" ]; then
+ rbenv_root="${HOME}/.rbenv"
+elif [ -s "/usr/local/rbenv" ]; then
+ rbenv_root="/usr/local/rbenv"
+ export RBENV_ROOT="$rbenv_root"
+fi
+
+if [ -n "$rbenv_root" ]; then
+ export PATH="${rbenv_root}/bin:$PATH"
+ eval "$(rbenv init -)"
+fi
- change mode from '' to '0755'
- change owner from '' to 'root'
Recipe: yum-epel::default
* yum_repository[epel] action create
* template[/etc/yum.repos.d/epel.repo] action create
- create new file /etc/yum.repos.d/epel.repo
- update content in file /etc/yum.repos.d/epel.repo from none to c7a666
--- /etc/yum.repos.d/epel.repo 2017-06-24 04:17:54.566680014 +0000
+++ /etc/yum.repos.d/.chef-epel20170624-171-vg208y.repo 2017-06-24 04:17:54.566680014 +0000
@@ -1 +1,12 @@
+# This file was generated by Chef
+# Do NOT modify this file by hand.
+
+[epel]
+name=Extra Packages for 7 - $basearch
+enabled=1
+failovermethod=priority
+fastestmirror_enabled=0
+gpgcheck=1
+gpgkey=https://download.fedoraproject.org/pub/epel/RPM-GPG-KEY-EPEL-7
+mirrorlist=http://mirrors.fedoraproject.org/mirrorlist?repo=epel-7&arch=$basearch
- change mode from '' to '0644'
* execute[yum clean metadata epel] action run
- execute yum clean metadata --disablerepo=* --enablerepo=epel
* execute[yum-makecache-epel] action run
- execute yum -q -y makecache --disablerepo=* --enablerepo=epel
* ruby_block[yum-cache-reload-epel] action create
- execute the ruby block yum-cache-reload-epel
* execute[yum clean metadata epel] action nothing (skipped due to action :nothing)
* execute[yum-makecache-epel] action nothing (skipped due to action :nothing)
* ruby_block[yum-cache-reload-epel] action nothing (skipped due to action :nothing)
Recipe: git::package
* git_client[default] action install
* yum_package[default :create git] action install (up to date)
(up to date)
Recipe: ruby_build::default
* yum_package[tar, bash, curl] action install (up to date)
* execute[Install ruby-build] action nothing (skipped due to action :nothing)
* directory[/tmp/kitchen/cache] action create (up to date)
* git[/tmp/kitchen/cache/ruby-build] action checkout
- clone from https://github.com/rbenv/ruby-build.git into /tmp/kitchen/cache/ruby-build
- checkout ref 476d09b66a14392989c3c65793428742e1d9f951 branch master
* execute[Install ruby-build] action run
- execute ./install.sh
Running handlers:
Running handlers complete
Chef Client finished, 12/21 resources updated in 36 seconds
Finished converging <default-centos-73> (0m57.52s).
-----> Setting up <default-centos-73>...
Finished setting up <default-centos-73> (0m0.00s).
-----> Verifying <default-centos-73>...
Loaded tests from test/smoke/default
Profile: tests from test/smoke/default
Version: (not specified)
Target: ssh://kitchen@localhost:32777
File /home/lita/.rbenv/bin/rbenv
∅ should exist
expected File /home/lita/.rbenv/bin/rbenv to exist
Group lita
✔ should exist
User lita
✔ should exist
✔ group should eq "lita"
✔ home should eq "/home/lita"
✔ shell should eq "/bin/bash"
File /home/lita
✔ should exist
✔ owner should eq "lita"
✔ group should eq "lita"
Test Summary: 8 successful, 1 failures, 0 skipped
>>>>>> ------Exception-------
>>>>>> Class: Kitchen::ActionFailed
>>>>>> Message: 1 actions failed.
>>>>>> Verify failed on instance <default-centos-73>. Please see .kitchen/logs/default-centos-73.log for more details
>>>>>> ----------------------
>>>>>> Please see .kitchen/logs/kitchen.log for more details
>>>>>> Also try running `kitchen diagnose --all` for configuration
```
|
defect
|
user installs not installing rbenv just rbenv install cookbook version chef client version platform details osx running docker ce version ce chef v chef development kit version chef client version delivery version master berks version kitchen version scenario install rbenv and a ruby for a specific user steps to reproduce include recipe rbenv ruby user install in a recipe and populate the node default with the example information but using ruby also including the recipes in the run list for kitchen yielded the same result cookbook excerpt node override user lita rubies global gems name bundler name rake name thor name lita node override include recipe ruby rbenv user include recipe ruby build expected result either rbenv should be installed or rbenv with ruby build plugin should be installed or a version of ruby after compiling which should take a significant amount of time actual result actual results below for some reason the only available commands relating to rbenv are rbenv install and rbenv uninstall but no actual rbenv thank you for installing chef transferring files to starting chef client version warn plugin network unable to detect ipaddress warn plugin network unable to detect ipaddress creating a new client identity for default centos using the validator key resolving cookbooks for run list synchronizing cookbooks wheatley cookbook redisio ruby build ruby rbenv build essential ulimit selinux policy yum epel seven zip git mingw compat resource dmg ohai windows installing cookbook gems compiling cookbooks converging resources recipe wheatley cookbook user setup group action create create group lita linux user action create create user lita directory action create create new directory home lita change owner from to lita change group from to lita recipe ruby rbenv user install yum package action install install version of package git yum package action install up to date template action create create new file etc profile d rbenv sh update content in file etc profile d rbenv sh from none to etc profile d rbenv sh etc profile d chef sh generated by chef for local modifications will be overridden prefer a user rbenv over a system wide install if then rbenv root home rbenv elif then rbenv root usr local rbenv export rbenv root rbenv root fi if then export path rbenv root bin path eval rbenv init fi change mode from to change owner from to root recipe yum epel default yum repository action create template action create create new file etc yum repos d epel repo update content in file etc yum repos d epel repo from none to etc yum repos d epel repo etc yum repos d chef repo this file was generated by chef do not modify this file by hand name extra packages for basearch enabled failovermethod priority fastestmirror enabled gpgcheck gpgkey mirrorlist change mode from to execute action run execute yum clean metadata disablerepo enablerepo epel execute action run execute yum q y makecache disablerepo enablerepo epel ruby block action create execute the ruby block yum cache reload epel execute action nothing skipped due to action nothing execute action nothing skipped due to action nothing ruby block action nothing skipped due to action nothing recipe git package git client action install yum package action install up to date up to date recipe ruby build default yum package action install up to date execute action nothing skipped due to action nothing directory action create up to date git action checkout clone from into tmp kitchen cache ruby build checkout ref branch master execute action run execute install sh running handlers running handlers complete chef client finished resources updated in seconds finished converging setting up finished setting up verifying loaded tests from test smoke default profile tests from test smoke default version not specified target ssh kitchen localhost file home lita rbenv bin rbenv ∅ should exist expected file home lita rbenv bin rbenv to exist group lita ✔ should exist user lita ✔ should exist ✔ group should eq lita ✔ home should eq home lita ✔ shell should eq bin bash file home lita ✔ should exist ✔ owner should eq lita ✔ group should eq lita test summary successful failures skipped exception class kitchen actionfailed message actions failed verify failed on instance please see kitchen logs default centos log for more details please see kitchen logs kitchen log for more details also try running kitchen diagnose all for configuration
| 1
|
71,996
| 23,889,107,439
|
IssuesEvent
|
2022-09-08 10:01:00
|
vector-im/element-web
|
https://api.github.com/repos/vector-im/element-web
|
closed
|
Images are not included inside exported messages history and has to be viewed separately
|
T-Defect S-Minor O-Occasional A-Export-Chat
|
### Steps to reproduce
1- Open any chat room in Element web
2- Click room info located at the top right corner of your screen
3- Click export chat
4- Choose format as HTML (from the beginning) then tick the "Include attachments" checkbox
5- The result is an archive that has many files one of them is called "messages.html"
6- Clicking this file will launch it in your browser, it has the full history of the chat room with videos included, but not images
7- If the user wanna see the images then he/she should open the images folder and watch every image separately
8- This move destroyed the context of the chat room
9- Why is there "messages.html" and "messages2.html"? Why not make the entire history in one file?
### Outcome
I expected to have the full room history exported and available for viewing in one html file with both images and videos included into that single file, so that I can open it in my browser and watch the whole history, what I got instead was an export distributed into two html files without any images, the images was available but standalone in a separate folder which ruined the context of the chat room.
### Operating system
Debian
### Browser information
Tested in both Firefox 91.6.0esr (64-bit) and Google Chrome 98.0.4758.80 (64-bit)
### URL for webapp
https://app.element.io/
### Application version
Element version: 1.10.11
### Homeserver
matrix.org
### Will you send logs?
No
|
1.0
|
Images are not included inside exported messages history and has to be viewed separately - ### Steps to reproduce
1- Open any chat room in Element web
2- Click room info located at the top right corner of your screen
3- Click export chat
4- Choose format as HTML (from the beginning) then tick the "Include attachments" checkbox
5- The result is an archive that has many files one of them is called "messages.html"
6- Clicking this file will launch it in your browser, it has the full history of the chat room with videos included, but not images
7- If the user wanna see the images then he/she should open the images folder and watch every image separately
8- This move destroyed the context of the chat room
9- Why is there "messages.html" and "messages2.html"? Why not make the entire history in one file?
### Outcome
I expected to have the full room history exported and available for viewing in one html file with both images and videos included into that single file, so that I can open it in my browser and watch the whole history, what I got instead was an export distributed into two html files without any images, the images was available but standalone in a separate folder which ruined the context of the chat room.
### Operating system
Debian
### Browser information
Tested in both Firefox 91.6.0esr (64-bit) and Google Chrome 98.0.4758.80 (64-bit)
### URL for webapp
https://app.element.io/
### Application version
Element version: 1.10.11
### Homeserver
matrix.org
### Will you send logs?
No
|
defect
|
images are not included inside exported messages history and has to be viewed separately steps to reproduce open any chat room in element web click room info located at the top right corner of your screen click export chat choose format as html from the beginning then tick the include attachments checkbox the result is an archive that has many files one of them is called messages html clicking this file will launch it in your browser it has the full history of the chat room with videos included but not images if the user wanna see the images then he she should open the images folder and watch every image separately this move destroyed the context of the chat room why is there messages html and html why not make the entire history in one file outcome i expected to have the full room history exported and available for viewing in one html file with both images and videos included into that single file so that i can open it in my browser and watch the whole history what i got instead was an export distributed into two html files without any images the images was available but standalone in a separate folder which ruined the context of the chat room operating system debian browser information tested in both firefox bit and google chrome bit url for webapp application version element version homeserver matrix org will you send logs no
| 1
|
43,630
| 11,782,109,737
|
IssuesEvent
|
2020-03-17 00:42:28
|
Cockatrice/Cockatrice
|
https://api.github.com/repos/Cockatrice/Cockatrice
|
closed
|
Scheme cards are not added
|
App - Oracle Defect - Regression
|
Many scheme cards are printed with a star in their collectors number as the only print, this means they are ignored.
|
1.0
|
Scheme cards are not added - Many scheme cards are printed with a star in their collectors number as the only print, this means they are ignored.
|
defect
|
scheme cards are not added many scheme cards are printed with a star in their collectors number as the only print this means they are ignored
| 1
|
42,338
| 10,967,548,585
|
IssuesEvent
|
2019-11-28 09:46:19
|
PowerDNS/pdns
|
https://api.github.com/repos/PowerDNS/pdns
|
closed
|
LUA record with view function can cause segfault
|
auth defect
|
- Program: Authoritative
- Issue type: Bug report
### Short description
Having a LUA record with this syntax causes a segfault in pdns
A "view({{{'10.0.0.0/8'}, {'10.100.15.3'}},{{'0.0.0.0/0'}, {nil}}})"
<!-- Explain in a few sentences what the issue/request is -->
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: Got a signal 11, attempting to print trace:
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /usr/sbin/pdns_server-instance(+0x2d1429) [0x560bf4530429]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /lib/x86_64-linux-gnu/libc.so.6(+0x354b0) [0x7f16458384b0]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /usr/sbin/pdns_server-instance(+0x38dba5) [0x560bf45ecba5]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /usr/lib/x86_64-linux-gnu/libluajit-5.1.so.2(+0x91a6) [0x7f16466941a6]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /usr/lib/x86_64-linux-gnu/libluajit-5.1.so.2(lua_pcall+0x30) [0x7f16466d9980]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /usr/sbin/pdns_server-instance(_ZN10LuaContext7callRawEP9lua_StateNS_12PushedObjectEi+0x3f) [0x560bf44872df]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /usr/sbin/pdns_server-instance(_Z8luaSynthRKNSt7__cxx1112basic_stringIcSt11char_traitsIcESaIcEEERK7DNSNameS9_iRK9DNSPackett+0x18eb) [0x560bf45eeb5b]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /usr/sbin/pdns_server-instance(_ZN13PacketHandler10doQuestionEP9DNSPacket+0x103b) [0x560bf452129b]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /usr/sbin/pdns_server-instance(_ZN13PacketHandler8questionEP9DNSPacket+0x81) [0x560bf4522cd1]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /usr/sbin/pdns_server-instance(_ZN22MultiThreadDistributorI9DNSPacketS0_13PacketHandlerE10makeThreadEPv+0x1a2) [0x560bf439d682]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /lib/x86_64-linux-gnu/libpthread.so.0(+0x76ba) [0x7f1645bd46ba]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /lib/x86_64-linux-gnu/libc.so.6(clone+0x6d) [0x7f164590a41d]
### Environment
- Operating system: Ubuntu 16.04
- Software version: pdns 4.2.0
- Software source: PowerDNS repository
### Steps to reproduce
Create the record above and query it to match the nil one
### Expected behaviour
servfail or nxdomain
### Actual behaviour
segfault
|
1.0
|
LUA record with view function can cause segfault - - Program: Authoritative
- Issue type: Bug report
### Short description
Having a LUA record with this syntax causes a segfault in pdns
A "view({{{'10.0.0.0/8'}, {'10.100.15.3'}},{{'0.0.0.0/0'}, {nil}}})"
<!-- Explain in a few sentences what the issue/request is -->
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: Got a signal 11, attempting to print trace:
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /usr/sbin/pdns_server-instance(+0x2d1429) [0x560bf4530429]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /lib/x86_64-linux-gnu/libc.so.6(+0x354b0) [0x7f16458384b0]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /usr/sbin/pdns_server-instance(+0x38dba5) [0x560bf45ecba5]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /usr/lib/x86_64-linux-gnu/libluajit-5.1.so.2(+0x91a6) [0x7f16466941a6]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /usr/lib/x86_64-linux-gnu/libluajit-5.1.so.2(lua_pcall+0x30) [0x7f16466d9980]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /usr/sbin/pdns_server-instance(_ZN10LuaContext7callRawEP9lua_StateNS_12PushedObjectEi+0x3f) [0x560bf44872df]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /usr/sbin/pdns_server-instance(_Z8luaSynthRKNSt7__cxx1112basic_stringIcSt11char_traitsIcESaIcEEERK7DNSNameS9_iRK9DNSPackett+0x18eb) [0x560bf45eeb5b]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /usr/sbin/pdns_server-instance(_ZN13PacketHandler10doQuestionEP9DNSPacket+0x103b) [0x560bf452129b]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /usr/sbin/pdns_server-instance(_ZN13PacketHandler8questionEP9DNSPacket+0x81) [0x560bf4522cd1]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /usr/sbin/pdns_server-instance(_ZN22MultiThreadDistributorI9DNSPacketS0_13PacketHandlerE10makeThreadEPv+0x1a2) [0x560bf439d682]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /lib/x86_64-linux-gnu/libpthread.so.0(+0x76ba) [0x7f1645bd46ba]
Nov 22 15:29:30 vm-powerdns3 pdns[1821]: /lib/x86_64-linux-gnu/libc.so.6(clone+0x6d) [0x7f164590a41d]
### Environment
- Operating system: Ubuntu 16.04
- Software version: pdns 4.2.0
- Software source: PowerDNS repository
### Steps to reproduce
Create the record above and query it to match the nil one
### Expected behaviour
servfail or nxdomain
### Actual behaviour
segfault
|
defect
|
lua record with view function can cause segfault program authoritative issue type bug report short description having a lua record with this syntax causes a segfault in pdns a view nil nov vm pdns got a signal attempting to print trace nov vm pdns usr sbin pdns server instance nov vm pdns lib linux gnu libc so nov vm pdns usr sbin pdns server instance nov vm pdns usr lib linux gnu libluajit so nov vm pdns usr lib linux gnu libluajit so lua pcall nov vm pdns usr sbin pdns server instance statens nov vm pdns usr sbin pdns server instance nov vm pdns usr sbin pdns server instance nov vm pdns usr sbin pdns server instance nov vm pdns usr sbin pdns server instance nov vm pdns lib linux gnu libpthread so nov vm pdns lib linux gnu libc so clone environment operating system ubuntu software version pdns software source powerdns repository steps to reproduce create the record above and query it to match the nil one expected behaviour servfail or nxdomain actual behaviour segfault
| 1
|
63,789
| 17,937,515,217
|
IssuesEvent
|
2021-09-10 17:17:40
|
avereon/carta
|
https://api.github.com/repos/avereon/carta
|
closed
|
Auto save after deleting layer caused IllegalStateException
|
bug / defect
|
IllegalStateException: Duplicate key null (attempted merging values {layers=[1ee775ba-30a4-4146-ab69-87f237748421, da655d30-c00c-4d5c-8d54-5cf296f4e83a, dbaa28cc-d0eb-4e99-88df-517dfd98a243, 98907219-428c-49e9-a612-e30267de7f88]} and {layers=[1ee775ba-30a4-4146-ab69-87f237748421, da655d30-c00c-4d5c-8d54-5cf296f4e83a, be0cfbe1-04db-4d50-a646-510cc04094fc, 4c7d9fe0-fc19-4e93-b43e-699572251cd4, 98907219-428c-49e9-a612-e30267de7f88]})
at java.base/java.util.stream.Collectors.duplicateKeyException(Collectors.java:135)
at java.base/java.util.stream.Collectors.lambda$uniqKeysMapAccumulator$1(Collectors.java:182)
at java.base/java.util.stream.ReduceOps$3ReducingSink.accept(ReduceOps.java:169)
at java.base/java.util.HashMap$KeySpliterator.forEachRemaining(HashMap.java:1694)
at java.base/java.util.stream.AbstractPipeline.copyInto(AbstractPipeline.java:484)
at java.base/java.util.stream.AbstractPipeline.wrapAndCopyInto(AbstractPipeline.java:474)
at java.base/java.util.stream.ReduceOps$ReduceOp.evaluateSequential(ReduceOps.java:913)
at java.base/java.util.stream.AbstractPipeline.evaluate(AbstractPipeline.java:234)
at java.base/java.util.stream.ReferencePipeline.collect(ReferencePipeline.java:682)
at com.avereon.cartesia/com.avereon.cartesia.CartesiaDesignCodec.mapDesign(CartesiaDesignCodec.java:251)
at com.avereon.cartesia/com.avereon.cartesia.CartesiaDesignCodec.save(CartesiaDesignCodec.java:118)
at com.avereon.xenon/com.avereon.xenon.scheme.FileScheme.save(FileScheme.java:72)
at com.avereon.xenon/com.avereon.xenon.asset.Asset.save(Asset.java:320)
at com.avereon.xenon/com.avereon.xenon.asset.AssetManager.doSaveAsset(AssetManager.java:1125)
at com.avereon.xenon/com.avereon.xenon.asset.AssetManager$SaveAssetTask.doOperation(AssetManager.java:1641)
at com.avereon.xenon/com.avereon.xenon.asset.AssetManager$AssetTask.call(AssetManager.java:1564)
at com.avereon.xenon/com.avereon.xenon.asset.AssetManager$AssetTask.call(AssetManager.java:1542)
at com.avereon.xenon/com.avereon.xenon.task.Task$TaskCallable.call(Task.java:317)
at java.base/java.util.concurrent.FutureTask.run(FutureTask.java:264)
at com.avereon.xenon/com.avereon.xenon.task.Task.run(Task.java:90)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1130)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:630)
at java.base/java.lang.Thread.run(Thread.java:831)
at com.avereon.xenon/com.avereon.xenon.task.TaskThread.run(TaskThread.java:16)
|
1.0
|
Auto save after deleting layer caused IllegalStateException - IllegalStateException: Duplicate key null (attempted merging values {layers=[1ee775ba-30a4-4146-ab69-87f237748421, da655d30-c00c-4d5c-8d54-5cf296f4e83a, dbaa28cc-d0eb-4e99-88df-517dfd98a243, 98907219-428c-49e9-a612-e30267de7f88]} and {layers=[1ee775ba-30a4-4146-ab69-87f237748421, da655d30-c00c-4d5c-8d54-5cf296f4e83a, be0cfbe1-04db-4d50-a646-510cc04094fc, 4c7d9fe0-fc19-4e93-b43e-699572251cd4, 98907219-428c-49e9-a612-e30267de7f88]})
at java.base/java.util.stream.Collectors.duplicateKeyException(Collectors.java:135)
at java.base/java.util.stream.Collectors.lambda$uniqKeysMapAccumulator$1(Collectors.java:182)
at java.base/java.util.stream.ReduceOps$3ReducingSink.accept(ReduceOps.java:169)
at java.base/java.util.HashMap$KeySpliterator.forEachRemaining(HashMap.java:1694)
at java.base/java.util.stream.AbstractPipeline.copyInto(AbstractPipeline.java:484)
at java.base/java.util.stream.AbstractPipeline.wrapAndCopyInto(AbstractPipeline.java:474)
at java.base/java.util.stream.ReduceOps$ReduceOp.evaluateSequential(ReduceOps.java:913)
at java.base/java.util.stream.AbstractPipeline.evaluate(AbstractPipeline.java:234)
at java.base/java.util.stream.ReferencePipeline.collect(ReferencePipeline.java:682)
at com.avereon.cartesia/com.avereon.cartesia.CartesiaDesignCodec.mapDesign(CartesiaDesignCodec.java:251)
at com.avereon.cartesia/com.avereon.cartesia.CartesiaDesignCodec.save(CartesiaDesignCodec.java:118)
at com.avereon.xenon/com.avereon.xenon.scheme.FileScheme.save(FileScheme.java:72)
at com.avereon.xenon/com.avereon.xenon.asset.Asset.save(Asset.java:320)
at com.avereon.xenon/com.avereon.xenon.asset.AssetManager.doSaveAsset(AssetManager.java:1125)
at com.avereon.xenon/com.avereon.xenon.asset.AssetManager$SaveAssetTask.doOperation(AssetManager.java:1641)
at com.avereon.xenon/com.avereon.xenon.asset.AssetManager$AssetTask.call(AssetManager.java:1564)
at com.avereon.xenon/com.avereon.xenon.asset.AssetManager$AssetTask.call(AssetManager.java:1542)
at com.avereon.xenon/com.avereon.xenon.task.Task$TaskCallable.call(Task.java:317)
at java.base/java.util.concurrent.FutureTask.run(FutureTask.java:264)
at com.avereon.xenon/com.avereon.xenon.task.Task.run(Task.java:90)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1130)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:630)
at java.base/java.lang.Thread.run(Thread.java:831)
at com.avereon.xenon/com.avereon.xenon.task.TaskThread.run(TaskThread.java:16)
|
defect
|
auto save after deleting layer caused illegalstateexception illegalstateexception duplicate key null attempted merging values layers and layers at java base java util stream collectors duplicatekeyexception collectors java at java base java util stream collectors lambda uniqkeysmapaccumulator collectors java at java base java util stream reduceops accept reduceops java at java base java util hashmap keyspliterator foreachremaining hashmap java at java base java util stream abstractpipeline copyinto abstractpipeline java at java base java util stream abstractpipeline wrapandcopyinto abstractpipeline java at java base java util stream reduceops reduceop evaluatesequential reduceops java at java base java util stream abstractpipeline evaluate abstractpipeline java at java base java util stream referencepipeline collect referencepipeline java at com avereon cartesia com avereon cartesia cartesiadesigncodec mapdesign cartesiadesigncodec java at com avereon cartesia com avereon cartesia cartesiadesigncodec save cartesiadesigncodec java at com avereon xenon com avereon xenon scheme filescheme save filescheme java at com avereon xenon com avereon xenon asset asset save asset java at com avereon xenon com avereon xenon asset assetmanager dosaveasset assetmanager java at com avereon xenon com avereon xenon asset assetmanager saveassettask dooperation assetmanager java at com avereon xenon com avereon xenon asset assetmanager assettask call assetmanager java at com avereon xenon com avereon xenon asset assetmanager assettask call assetmanager java at com avereon xenon com avereon xenon task task taskcallable call task java at java base java util concurrent futuretask run futuretask java at com avereon xenon com avereon xenon task task run task java at java base java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java base java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java base java lang thread run thread java at com avereon xenon com avereon xenon task taskthread run taskthread java
| 1
|
55,179
| 14,258,742,878
|
IssuesEvent
|
2020-11-20 06:55:47
|
DependencyTrack/dependency-track
|
https://api.github.com/repos/DependencyTrack/dependency-track
|
closed
|
InternalAnalyzer not associating vulnerabilities for CPE
|
defect p1 pending release
|
### Current Behavior:
Analysis Fails because the Component only has a CPE in QueryManager.matchIdentity(). Operating Systems won't ever have a purl as far as I can tell.
### Steps to Reproduce:
``` xml
<component type="operating-system">
<name>kernel-4.19.78-yocto-standard</name>
<version>4.19.69</version>
<cpe>cpe:2.3:o:linux:linux_kernel:4.19.69:*:*:*:*:*:*:*</cpe>
</component>
```
### Expected Behavior:
in version 3.8.0 299 Vulnerabilities are associated
### Environment:
- Dependency-Track Version: 4.0.0-SNAPSHOT
- Distribution: Docker
- BOM Format & Version: CycloneDX XML 1.2
- Database Server: H2
- Browser: Chrome
### Additional Details:
```
java.lang.NullPointerException: null
at org.dependencytrack.persistence.QueryManager.matchIdentity(QueryManager.java:1706)
at org.dependencytrack.util.NotificationUtil.analyzeNotificationCriteria(NotificationUtil.java:51)
at org.dependencytrack.tasks.scanners.AbstractVulnerableSoftwareAnalysisTask.analyzeVersionRange(AbstractVulnerableSoftwareAnalysisTask.java:58)
at org.dependencytrack.tasks.scanners.InternalAnalysisTask.versionRangeAnalysis(InternalAnalysisTask.java:104)
at org.dependencytrack.tasks.scanners.InternalAnalysisTask.analyze(InternalAnalysisTask.java:86)
at org.dependencytrack.tasks.scanners.InternalAnalysisTask.inform(InternalAnalysisTask.java:59)
at org.dependencytrack.tasks.VulnerabilityAnalysisTask.performAnalysis(VulnerabilityAnalysisTask.java:148)
at org.dependencytrack.tasks.VulnerabilityAnalysisTask.inform(VulnerabilityAnalysisTask.java:103)
at alpine.event.framework.BaseEventService.lambda$publish$0(BaseEventService.java:99)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at java.base/java.lang.Thread.run(Thread.java:834)
```
If I attempt to use a ternary `query.executeWithArray(cid.getPurl() == null ? null : cid.getPurl().canonicalize(), ` to fix the purl NPE I get this instead which is way over my head.
```
org.datanucleus.exceptions.NucleusUserException: Object with id "3696" is managed by a different persistence manager
at org.datanucleus.ExecutionContextImpl.findObjectProvider(ExecutionContextImpl.java:1276)
at org.datanucleus.store.rdbms.scostore.ElementContainerStore.validateElementForWriting(ElementContainerStore.java:283)
at org.datanucleus.store.rdbms.scostore.JoinListStore.internalAdd(JoinListStore.java:200)
at org.datanucleus.store.rdbms.scostore.AbstractListStore.add(AbstractListStore.java:113)
at org.datanucleus.store.types.wrappers.backed.List.add(List.java:647)
at org.dependencytrack.model.Component.addVulnerability(Component.java:593)
at org.dependencytrack.persistence.QueryManager.addVulnerability(QueryManager.java:1402)
at org.dependencytrack.persistence.QueryManager.addVulnerability(QueryManager.java:1388)
at org.dependencytrack.tasks.scanners.AbstractVulnerableSoftwareAnalysisTask.analyzeVersionRange(AbstractVulnerableSoftwareAnalysisTask.java:59)
at org.dependencytrack.tasks.scanners.InternalAnalysisTask.versionRangeAnalysis(InternalAnalysisTask.java:104)
at org.dependencytrack.tasks.scanners.InternalAnalysisTask.analyze(InternalAnalysisTask.java:86)
at org.dependencytrack.tasks.scanners.InternalAnalysisTask.inform(InternalAnalysisTask.java:59)
at org.dependencytrack.tasks.VulnerabilityAnalysisTask.performAnalysis(VulnerabilityAnalysisTask.java:148)
at org.dependencytrack.tasks.VulnerabilityAnalysisTask.inform(VulnerabilityAnalysisTask.java:103)
at alpine.event.framework.BaseEventService.lambda$publish$0(BaseEventService.java:99)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at java.base/java.lang.Thread.run(Thread.java:834)
```
|
1.0
|
InternalAnalyzer not associating vulnerabilities for CPE - ### Current Behavior:
Analysis Fails because the Component only has a CPE in QueryManager.matchIdentity(). Operating Systems won't ever have a purl as far as I can tell.
### Steps to Reproduce:
``` xml
<component type="operating-system">
<name>kernel-4.19.78-yocto-standard</name>
<version>4.19.69</version>
<cpe>cpe:2.3:o:linux:linux_kernel:4.19.69:*:*:*:*:*:*:*</cpe>
</component>
```
### Expected Behavior:
in version 3.8.0 299 Vulnerabilities are associated
### Environment:
- Dependency-Track Version: 4.0.0-SNAPSHOT
- Distribution: Docker
- BOM Format & Version: CycloneDX XML 1.2
- Database Server: H2
- Browser: Chrome
### Additional Details:
```
java.lang.NullPointerException: null
at org.dependencytrack.persistence.QueryManager.matchIdentity(QueryManager.java:1706)
at org.dependencytrack.util.NotificationUtil.analyzeNotificationCriteria(NotificationUtil.java:51)
at org.dependencytrack.tasks.scanners.AbstractVulnerableSoftwareAnalysisTask.analyzeVersionRange(AbstractVulnerableSoftwareAnalysisTask.java:58)
at org.dependencytrack.tasks.scanners.InternalAnalysisTask.versionRangeAnalysis(InternalAnalysisTask.java:104)
at org.dependencytrack.tasks.scanners.InternalAnalysisTask.analyze(InternalAnalysisTask.java:86)
at org.dependencytrack.tasks.scanners.InternalAnalysisTask.inform(InternalAnalysisTask.java:59)
at org.dependencytrack.tasks.VulnerabilityAnalysisTask.performAnalysis(VulnerabilityAnalysisTask.java:148)
at org.dependencytrack.tasks.VulnerabilityAnalysisTask.inform(VulnerabilityAnalysisTask.java:103)
at alpine.event.framework.BaseEventService.lambda$publish$0(BaseEventService.java:99)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at java.base/java.lang.Thread.run(Thread.java:834)
```
If I attempt to use a ternary `query.executeWithArray(cid.getPurl() == null ? null : cid.getPurl().canonicalize(), ` to fix the purl NPE I get this instead which is way over my head.
```
org.datanucleus.exceptions.NucleusUserException: Object with id "3696" is managed by a different persistence manager
at org.datanucleus.ExecutionContextImpl.findObjectProvider(ExecutionContextImpl.java:1276)
at org.datanucleus.store.rdbms.scostore.ElementContainerStore.validateElementForWriting(ElementContainerStore.java:283)
at org.datanucleus.store.rdbms.scostore.JoinListStore.internalAdd(JoinListStore.java:200)
at org.datanucleus.store.rdbms.scostore.AbstractListStore.add(AbstractListStore.java:113)
at org.datanucleus.store.types.wrappers.backed.List.add(List.java:647)
at org.dependencytrack.model.Component.addVulnerability(Component.java:593)
at org.dependencytrack.persistence.QueryManager.addVulnerability(QueryManager.java:1402)
at org.dependencytrack.persistence.QueryManager.addVulnerability(QueryManager.java:1388)
at org.dependencytrack.tasks.scanners.AbstractVulnerableSoftwareAnalysisTask.analyzeVersionRange(AbstractVulnerableSoftwareAnalysisTask.java:59)
at org.dependencytrack.tasks.scanners.InternalAnalysisTask.versionRangeAnalysis(InternalAnalysisTask.java:104)
at org.dependencytrack.tasks.scanners.InternalAnalysisTask.analyze(InternalAnalysisTask.java:86)
at org.dependencytrack.tasks.scanners.InternalAnalysisTask.inform(InternalAnalysisTask.java:59)
at org.dependencytrack.tasks.VulnerabilityAnalysisTask.performAnalysis(VulnerabilityAnalysisTask.java:148)
at org.dependencytrack.tasks.VulnerabilityAnalysisTask.inform(VulnerabilityAnalysisTask.java:103)
at alpine.event.framework.BaseEventService.lambda$publish$0(BaseEventService.java:99)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at java.base/java.lang.Thread.run(Thread.java:834)
```
|
defect
|
internalanalyzer not associating vulnerabilities for cpe current behavior analysis fails because the component only has a cpe in querymanager matchidentity operating systems won t ever have a purl as far as i can tell steps to reproduce xml kernel yocto standard cpe o linux linux kernel expected behavior in version vulnerabilities are associated environment dependency track version snapshot distribution docker bom format version cyclonedx xml database server browser chrome additional details java lang nullpointerexception null at org dependencytrack persistence querymanager matchidentity querymanager java at org dependencytrack util notificationutil analyzenotificationcriteria notificationutil java at org dependencytrack tasks scanners abstractvulnerablesoftwareanalysistask analyzeversionrange abstractvulnerablesoftwareanalysistask java at org dependencytrack tasks scanners internalanalysistask versionrangeanalysis internalanalysistask java at org dependencytrack tasks scanners internalanalysistask analyze internalanalysistask java at org dependencytrack tasks scanners internalanalysistask inform internalanalysistask java at org dependencytrack tasks vulnerabilityanalysistask performanalysis vulnerabilityanalysistask java at org dependencytrack tasks vulnerabilityanalysistask inform vulnerabilityanalysistask java at alpine event framework baseeventservice lambda publish baseeventservice java at java base java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java base java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java base java lang thread run thread java if i attempt to use a ternary query executewitharray cid getpurl null null cid getpurl canonicalize to fix the purl npe i get this instead which is way over my head org datanucleus exceptions nucleususerexception object with id is managed by a different persistence manager at org datanucleus executioncontextimpl findobjectprovider executioncontextimpl java at org datanucleus store rdbms scostore elementcontainerstore validateelementforwriting elementcontainerstore java at org datanucleus store rdbms scostore joinliststore internaladd joinliststore java at org datanucleus store rdbms scostore abstractliststore add abstractliststore java at org datanucleus store types wrappers backed list add list java at org dependencytrack model component addvulnerability component java at org dependencytrack persistence querymanager addvulnerability querymanager java at org dependencytrack persistence querymanager addvulnerability querymanager java at org dependencytrack tasks scanners abstractvulnerablesoftwareanalysistask analyzeversionrange abstractvulnerablesoftwareanalysistask java at org dependencytrack tasks scanners internalanalysistask versionrangeanalysis internalanalysistask java at org dependencytrack tasks scanners internalanalysistask analyze internalanalysistask java at org dependencytrack tasks scanners internalanalysistask inform internalanalysistask java at org dependencytrack tasks vulnerabilityanalysistask performanalysis vulnerabilityanalysistask java at org dependencytrack tasks vulnerabilityanalysistask inform vulnerabilityanalysistask java at alpine event framework baseeventservice lambda publish baseeventservice java at java base java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java base java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java base java lang thread run thread java
| 1
|
45,894
| 13,055,816,994
|
IssuesEvent
|
2020-07-30 02:49:30
|
icecube-trac/tix2
|
https://api.github.com/repos/icecube-trac/tix2
|
opened
|
compiling IceVer with suse 11 and gcc 4.3.2 (Trac #210)
|
IceVer Incomplete Migration Migrated from Trac defect
|
Migrated from https://code.icecube.wisc.edu/ticket/210
```json
{
"status": "closed",
"changetime": "2010-09-02T20:52:14",
"description": "{{{\n\nTo: dataclass\nSubject: [dataclass] compiling IceVer with suse 11 and gcc 4.3.2\nDate: Wed, 1 Sep 2010 10:25:50 +0200\n\nHi,\nI'm not sure if this is the right list but it can't be totally wrong.\n\nI'm doing simulation production on a cluster running suse 11 and gcc 4.3.2\nand I had some problems compiling IceVer/V03-00-03_sim which I hadn't when\nit was suse 10 and gcc 4.1.2\n\n1. cmake sets 'CURSES_NCURSES_INCLUDE_PATH:PATH=/usr/include/' but the\nncurses files are in '/usr/include/ncurses' and there are no links, so I had\nto change it in the CMakeCache.txt\n\n2. map.h could not be found. To solve this I changed '#include \"map.h\"' to\n'#include <map>' in\n'IceVer/V03-00-03_sim/src/interstring-verification/private/avgTDP/avgTDP.cxx'\nand\n'IceVer/V03-00-03_sim/src/interstring-verification/private/cmpTDP/cmpTDP.cxx'\n\n3. vector.h could not be found. Same solution as with map.h: '#include\n\"vector.h\"' --> '#include <vector>' in\n'V03-00-03_sim/src/toptiming-verification/public/toptiming-verification/reco/I3TopCombiFitParams.h'\n\nFor 2&3 I first tried adding the paths where the files are to $CPATH, but\nthis ended up in a 'includes nested to deeply' error.\n\nAfter this modifications compiling works fine and simulation doesn't throw\nany errors.\n\nNevertheless there lots of warnings about functions which will not be\nsupport in the future:\n\n/usr/include/c++/4.3/backward/backward_warning.h:33:2: warning: #warning\nThis\nfile includes at least one deprecated or antiquated header which may be\nremoved without further notice at a future date. Please use a non-\ndeprecated interface with equivalent functionality instead. For a listing\nof replacement headers and interfaces, consult the file backward_warning.h.\nTo disable this warning use -Wno-deprecated.\n\n",
"reporter": "nega",
"cc": "",
"resolution": "fixed",
"_ts": "1283460734000000",
"component": "IceVer",
"summary": "compiling IceVer with suse 11 and gcc 4.3.2",
"priority": "normal",
"keywords": "",
"time": "2010-09-02T20:33:50",
"milestone": "",
"owner": "",
"type": "defect"
}
```
|
1.0
|
compiling IceVer with suse 11 and gcc 4.3.2 (Trac #210) - Migrated from https://code.icecube.wisc.edu/ticket/210
```json
{
"status": "closed",
"changetime": "2010-09-02T20:52:14",
"description": "{{{\n\nTo: dataclass\nSubject: [dataclass] compiling IceVer with suse 11 and gcc 4.3.2\nDate: Wed, 1 Sep 2010 10:25:50 +0200\n\nHi,\nI'm not sure if this is the right list but it can't be totally wrong.\n\nI'm doing simulation production on a cluster running suse 11 and gcc 4.3.2\nand I had some problems compiling IceVer/V03-00-03_sim which I hadn't when\nit was suse 10 and gcc 4.1.2\n\n1. cmake sets 'CURSES_NCURSES_INCLUDE_PATH:PATH=/usr/include/' but the\nncurses files are in '/usr/include/ncurses' and there are no links, so I had\nto change it in the CMakeCache.txt\n\n2. map.h could not be found. To solve this I changed '#include \"map.h\"' to\n'#include <map>' in\n'IceVer/V03-00-03_sim/src/interstring-verification/private/avgTDP/avgTDP.cxx'\nand\n'IceVer/V03-00-03_sim/src/interstring-verification/private/cmpTDP/cmpTDP.cxx'\n\n3. vector.h could not be found. Same solution as with map.h: '#include\n\"vector.h\"' --> '#include <vector>' in\n'V03-00-03_sim/src/toptiming-verification/public/toptiming-verification/reco/I3TopCombiFitParams.h'\n\nFor 2&3 I first tried adding the paths where the files are to $CPATH, but\nthis ended up in a 'includes nested to deeply' error.\n\nAfter this modifications compiling works fine and simulation doesn't throw\nany errors.\n\nNevertheless there lots of warnings about functions which will not be\nsupport in the future:\n\n/usr/include/c++/4.3/backward/backward_warning.h:33:2: warning: #warning\nThis\nfile includes at least one deprecated or antiquated header which may be\nremoved without further notice at a future date. Please use a non-\ndeprecated interface with equivalent functionality instead. For a listing\nof replacement headers and interfaces, consult the file backward_warning.h.\nTo disable this warning use -Wno-deprecated.\n\n",
"reporter": "nega",
"cc": "",
"resolution": "fixed",
"_ts": "1283460734000000",
"component": "IceVer",
"summary": "compiling IceVer with suse 11 and gcc 4.3.2",
"priority": "normal",
"keywords": "",
"time": "2010-09-02T20:33:50",
"milestone": "",
"owner": "",
"type": "defect"
}
```
|
defect
|
compiling icever with suse and gcc trac migrated from json status closed changetime description n nto dataclass nsubject compiling icever with suse and gcc ndate wed sep n nhi ni m not sure if this is the right list but it can t be totally wrong n ni m doing simulation production on a cluster running suse and gcc nand i had some problems compiling icever sim which i hadn t when nit was suse and gcc n cmake sets curses ncurses include path path usr include but the nncurses files are in usr include ncurses and there are no links so i had nto change it in the cmakecache txt n map h could not be found to solve this i changed include map h to n include in n icever sim src interstring verification private avgtdp avgtdp cxx nand n icever sim src interstring verification private cmptdp cmptdp cxx n vector h could not be found same solution as with map h include n vector h include in n sim src toptiming verification public toptiming verification reco h n nfor i first tried adding the paths where the files are to cpath but nthis ended up in a includes nested to deeply error n nafter this modifications compiling works fine and simulation doesn t throw nany errors n nnevertheless there lots of warnings about functions which will not be nsupport in the future n n usr include c backward backward warning h warning warning nthis nfile includes at least one deprecated or antiquated header which may be nremoved without further notice at a future date please use a non ndeprecated interface with equivalent functionality instead for a listing nof replacement headers and interfaces consult the file backward warning h nto disable this warning use wno deprecated n n reporter nega cc resolution fixed ts component icever summary compiling icever with suse and gcc priority normal keywords time milestone owner type defect
| 1
|
102,586
| 8,849,706,054
|
IssuesEvent
|
2019-01-08 11:00:43
|
researchstudio-sat/webofneeds
|
https://api.github.com/repos/researchstudio-sat/webofneeds
|
closed
|
Personas take forever to load
|
testing
|
When opening the settings UI, existing personas do not get loaded for a considerable amount of time.
|
1.0
|
Personas take forever to load - When opening the settings UI, existing personas do not get loaded for a considerable amount of time.
|
non_defect
|
personas take forever to load when opening the settings ui existing personas do not get loaded for a considerable amount of time
| 0
|
35,021
| 7,886,349,417
|
IssuesEvent
|
2018-06-27 15:00:55
|
mozilla/addons-frontend
|
https://api.github.com/repos/mozilla/addons-frontend
|
closed
|
Create eslint plugin to prevent tagged template literals being used for localization
|
component: code quality component: i18n priority: p4 project: amo size: M triaged
|
The new set-up for multi-line strings for extraction and gettext calls requires template literal tags to be not tagged and leading whitespace in multiline template literals is implicitly removed.
Since a tagged template literal will not be extractable we could use a eslint plugin to flag a tagged template literal inside any gettext calls.
|
1.0
|
Create eslint plugin to prevent tagged template literals being used for localization - The new set-up for multi-line strings for extraction and gettext calls requires template literal tags to be not tagged and leading whitespace in multiline template literals is implicitly removed.
Since a tagged template literal will not be extractable we could use a eslint plugin to flag a tagged template literal inside any gettext calls.
|
non_defect
|
create eslint plugin to prevent tagged template literals being used for localization the new set up for multi line strings for extraction and gettext calls requires template literal tags to be not tagged and leading whitespace in multiline template literals is implicitly removed since a tagged template literal will not be extractable we could use a eslint plugin to flag a tagged template literal inside any gettext calls
| 0
|
62,791
| 17,196,954,854
|
IssuesEvent
|
2021-07-16 18:58:39
|
vector-im/element-web
|
https://api.github.com/repos/vector-im/element-web
|
closed
|
reliable repro: duplicates in new room list
|
A-Room-List P1 S-Major T-Defect X-Cannot-Reproduce Z-TravisR
|
### Description
I can reliably repro duplicates in the new room list. This repro'd on /develop and now repros on app.element.io.
### Steps to reproduce
1) (not sure if necessary) Have a bunch of rooms.
2) it doesn't seem to matter which lists are collapsed or expanded
3) click on a low priority room so that it's visible/active
4) right click on the room, make it a favorite
5) click on any other room
6) expand/look at the favorite list, it will have at least two copies of the newly favorited room.
Often from this point on the list is just broken and requires a reload. Seems like some messy state somewhere.
<!-- Include screenshots if possible: you can drag and drop images below. -->
### Version information
- **Platform**: **web (in-browser)**
In this screenshot, I did the repro instructions:
1) I was in `Rust (lang)` (the orange icon).
2) I changed it's priority.
3) It didn't move. It wouldn't move. I collapsed the Favorite list
4) I clicked on an old room i nteh room list.
5) All of the sudden `Rust (lang)` disappeared from Low Priority
6) I expanded the Favorite list and this is what it looked like:

For the web app:
- **Browser**: Firefox
- **OS**: NixOS
- **URL**: app.element.io
|
1.0
|
reliable repro: duplicates in new room list - ### Description
I can reliably repro duplicates in the new room list. This repro'd on /develop and now repros on app.element.io.
### Steps to reproduce
1) (not sure if necessary) Have a bunch of rooms.
2) it doesn't seem to matter which lists are collapsed or expanded
3) click on a low priority room so that it's visible/active
4) right click on the room, make it a favorite
5) click on any other room
6) expand/look at the favorite list, it will have at least two copies of the newly favorited room.
Often from this point on the list is just broken and requires a reload. Seems like some messy state somewhere.
<!-- Include screenshots if possible: you can drag and drop images below. -->
### Version information
- **Platform**: **web (in-browser)**
In this screenshot, I did the repro instructions:
1) I was in `Rust (lang)` (the orange icon).
2) I changed it's priority.
3) It didn't move. It wouldn't move. I collapsed the Favorite list
4) I clicked on an old room i nteh room list.
5) All of the sudden `Rust (lang)` disappeared from Low Priority
6) I expanded the Favorite list and this is what it looked like:

For the web app:
- **Browser**: Firefox
- **OS**: NixOS
- **URL**: app.element.io
|
defect
|
reliable repro duplicates in new room list description i can reliably repro duplicates in the new room list this repro d on develop and now repros on app element io steps to reproduce not sure if necessary have a bunch of rooms it doesn t seem to matter which lists are collapsed or expanded click on a low priority room so that it s visible active right click on the room make it a favorite click on any other room expand look at the favorite list it will have at least two copies of the newly favorited room often from this point on the list is just broken and requires a reload seems like some messy state somewhere version information platform web in browser in this screenshot i did the repro instructions i was in rust lang the orange icon i changed it s priority it didn t move it wouldn t move i collapsed the favorite list i clicked on an old room i nteh room list all of the sudden rust lang disappeared from low priority i expanded the favorite list and this is what it looked like for the web app browser firefox os nixos url app element io
| 1
|
31,886
| 6,655,778,233
|
IssuesEvent
|
2017-09-29 17:50:04
|
jccastillo0007/eFacturaT
|
https://api.github.com/repos/jccastillo0007/eFacturaT
|
closed
|
Web CFDi3.3 - Tipo de Comprobante - Nodo impuestos
|
bug defect
|
El nodo impuestos no debe existir si el tipo de comprobante es T, P, N
|
1.0
|
Web CFDi3.3 - Tipo de Comprobante - Nodo impuestos - El nodo impuestos no debe existir si el tipo de comprobante es T, P, N
|
defect
|
web tipo de comprobante nodo impuestos el nodo impuestos no debe existir si el tipo de comprobante es t p n
| 1
|
49,710
| 13,187,254,963
|
IssuesEvent
|
2020-08-13 02:50:15
|
icecube-trac/tix3
|
https://api.github.com/repos/icecube-trac/tix3
|
opened
|
[cmake] python3 and the shebang (Trac #1912)
|
Incomplete Migration Migrated from Trac cmake defect
|
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1912">https://code.icecube.wisc.edu/ticket/1912</a>, reported by david.schultz and owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-09-18T05:50:20",
"description": "If you build cmake with a python binary that isn't called `python`, such as `python3`, then `icetray-inspect` fails. Likely `dataio-pyshovel` and other python scripts fail too.\n\nI guess the solution is to modify the shebang of all python executables as a cmake step? Something like:\nhttps://github.com/ros/catkin/pull/574/files",
"reporter": "david.schultz",
"cc": "kjmeagher",
"resolution": "worksforme",
"_ts": "1568785820929050",
"component": "cmake",
"summary": "[cmake] python3 and the shebang",
"priority": "normal",
"keywords": "",
"time": "2016-11-17T22:54:14",
"milestone": "Long-Term Future",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
|
1.0
|
[cmake] python3 and the shebang (Trac #1912) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1912">https://code.icecube.wisc.edu/ticket/1912</a>, reported by david.schultz and owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-09-18T05:50:20",
"description": "If you build cmake with a python binary that isn't called `python`, such as `python3`, then `icetray-inspect` fails. Likely `dataio-pyshovel` and other python scripts fail too.\n\nI guess the solution is to modify the shebang of all python executables as a cmake step? Something like:\nhttps://github.com/ros/catkin/pull/574/files",
"reporter": "david.schultz",
"cc": "kjmeagher",
"resolution": "worksforme",
"_ts": "1568785820929050",
"component": "cmake",
"summary": "[cmake] python3 and the shebang",
"priority": "normal",
"keywords": "",
"time": "2016-11-17T22:54:14",
"milestone": "Long-Term Future",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
|
defect
|
and the shebang trac migrated from json status closed changetime description if you build cmake with a python binary that isn t called python such as then icetray inspect fails likely dataio pyshovel and other python scripts fail too n ni guess the solution is to modify the shebang of all python executables as a cmake step something like n reporter david schultz cc kjmeagher resolution worksforme ts component cmake summary and the shebang priority normal keywords time milestone long term future owner nega type defect
| 1
|
26,259
| 4,643,366,335
|
IssuesEvent
|
2016-09-30 13:16:31
|
SeleniumHQ/selenium
|
https://api.github.com/repos/SeleniumHQ/selenium
|
closed
|
Provide shim for submitting form command
|
C-dotnet C-java C-nodejs C-py C-rb D-marionette G-w3c I-defect
|
The W3C WebDriver specification does not specify a command for submitting a form. Many language bindings in Selenium provide a `webElement.submit()` function that no longer has a corresponding primitive in the remote end.
Selenium will need to provide a shim for submitting a form.
Given an HTML form,
```html
<form>
<input>
<input type=submit>
</form>
```
one could imagine the workaround looking at `element.form.submit()` through JavaScript.
|
1.0
|
Provide shim for submitting form command - The W3C WebDriver specification does not specify a command for submitting a form. Many language bindings in Selenium provide a `webElement.submit()` function that no longer has a corresponding primitive in the remote end.
Selenium will need to provide a shim for submitting a form.
Given an HTML form,
```html
<form>
<input>
<input type=submit>
</form>
```
one could imagine the workaround looking at `element.form.submit()` through JavaScript.
|
defect
|
provide shim for submitting form command the webdriver specification does not specify a command for submitting a form many language bindings in selenium provide a webelement submit function that no longer has a corresponding primitive in the remote end selenium will need to provide a shim for submitting a form given an html form html one could imagine the workaround looking at element form submit through javascript
| 1
|
104,252
| 16,613,555,433
|
IssuesEvent
|
2021-06-02 14:15:00
|
Thanraj/linux-4.1.15
|
https://api.github.com/repos/Thanraj/linux-4.1.15
|
opened
|
CVE-2017-17864 (Low) detected in linux-stable-rtv4.1.33
|
security vulnerability
|
## CVE-2017-17864 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/Thanraj/linux-4.1.15/commits/5e3fb3e332499e1ad10a0969e55582af1027b085">5e3fb3e332499e1ad10a0969e55582af1027b085</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>linux-4.1.15/kernel/bpf/verifier.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>linux-4.1.15/kernel/bpf/verifier.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
kernel/bpf/verifier.c in the Linux kernel through 4.14.8 mishandles states_equal comparisons between the pointer data type and the UNKNOWN_VALUE data type, which allows local users to obtain potentially sensitive address information, aka a "pointer leak."
<p>Publish Date: 2017-12-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-17864>CVE-2017-17864</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-17864">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-17864</a></p>
<p>Release Date: 2017-12-27</p>
<p>Fix Resolution: v4.15-rc5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2017-17864 (Low) detected in linux-stable-rtv4.1.33 - ## CVE-2017-17864 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/Thanraj/linux-4.1.15/commits/5e3fb3e332499e1ad10a0969e55582af1027b085">5e3fb3e332499e1ad10a0969e55582af1027b085</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>linux-4.1.15/kernel/bpf/verifier.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>linux-4.1.15/kernel/bpf/verifier.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
kernel/bpf/verifier.c in the Linux kernel through 4.14.8 mishandles states_equal comparisons between the pointer data type and the UNKNOWN_VALUE data type, which allows local users to obtain potentially sensitive address information, aka a "pointer leak."
<p>Publish Date: 2017-12-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-17864>CVE-2017-17864</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-17864">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-17864</a></p>
<p>Release Date: 2017-12-27</p>
<p>Fix Resolution: v4.15-rc5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve low detected in linux stable cve low severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files linux kernel bpf verifier c linux kernel bpf verifier c vulnerability details kernel bpf verifier c in the linux kernel through mishandles states equal comparisons between the pointer data type and the unknown value data type which allows local users to obtain potentially sensitive address information aka a pointer leak publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource
| 0
|
39,526
| 9,529,863,932
|
IssuesEvent
|
2019-04-29 12:32:23
|
primefaces/primefaces
|
https://api.github.com/repos/primefaces/primefaces
|
closed
|
Calendar: Popup mode with date/time pattern, sliders don't render properly when supplied with Date object with date and time
|
defect duplicate
|
## 1) Environment
- PrimeFaces version: 6.2.19 and 7.0.1
- Does it work on the newest released PrimeFaces version? No
- Does it work on the newest sources in GitHub? No
- Application server + version: Jetty (irrelevant)
- Affected browsers: all
## 2) Expected behavior
The time-part of a date is correctly displayed in a p:calendar component when using the popup mode.
## 3) Actual behavior
When the date object from a backing bean for a p:calendar contains a time, the time display shows "00:00:00" and all the sliders are on the left border, also representing "0".
## 4) Steps to reproduce
In calendar.xhtml from the sample, replace
`<p:calendar id="datetime" value="#{calendarView.date10}" pattern="MM/dd/yyyy HH:mm:ss" />`
with
`<p:calendar id="datetime" value="#{session.lastAccessedTime}" pattern="MM/dd/yyyy HH:mm:ss" />`
Now click in the calendar input field and have a look at the popup.
## 5) Sample XHTML
See above.
## 6) Sample bean
No changes necessary.
The problem probably has been introduced by fixing https://github.com/primefaces/primefaces/issues/3765. Fixing the issue for the inline mode introduced the exact same problem for the popup mode.
|
1.0
|
Calendar: Popup mode with date/time pattern, sliders don't render properly when supplied with Date object with date and time - ## 1) Environment
- PrimeFaces version: 6.2.19 and 7.0.1
- Does it work on the newest released PrimeFaces version? No
- Does it work on the newest sources in GitHub? No
- Application server + version: Jetty (irrelevant)
- Affected browsers: all
## 2) Expected behavior
The time-part of a date is correctly displayed in a p:calendar component when using the popup mode.
## 3) Actual behavior
When the date object from a backing bean for a p:calendar contains a time, the time display shows "00:00:00" and all the sliders are on the left border, also representing "0".
## 4) Steps to reproduce
In calendar.xhtml from the sample, replace
`<p:calendar id="datetime" value="#{calendarView.date10}" pattern="MM/dd/yyyy HH:mm:ss" />`
with
`<p:calendar id="datetime" value="#{session.lastAccessedTime}" pattern="MM/dd/yyyy HH:mm:ss" />`
Now click in the calendar input field and have a look at the popup.
## 5) Sample XHTML
See above.
## 6) Sample bean
No changes necessary.
The problem probably has been introduced by fixing https://github.com/primefaces/primefaces/issues/3765. Fixing the issue for the inline mode introduced the exact same problem for the popup mode.
|
defect
|
calendar popup mode with date time pattern sliders don t render properly when supplied with date object with date and time environment primefaces version and does it work on the newest released primefaces version no does it work on the newest sources in github no application server version jetty irrelevant affected browsers all expected behavior the time part of a date is correctly displayed in a p calendar component when using the popup mode actual behavior when the date object from a backing bean for a p calendar contains a time the time display shows and all the sliders are on the left border also representing steps to reproduce in calendar xhtml from the sample replace with now click in the calendar input field and have a look at the popup sample xhtml see above sample bean no changes necessary the problem probably has been introduced by fixing fixing the issue for the inline mode introduced the exact same problem for the popup mode
| 1
|
14,147
| 2,789,937,234
|
IssuesEvent
|
2015-05-08 22:33:04
|
google/google-visualization-api-issues
|
https://api.github.com/repos/google/google-visualization-api-issues
|
closed
|
docs refer to Macromedia website
|
Type-Defect
|
Original [issue 573](https://code.google.com/p/google-visualization-api-issues/issues/detail?id=573) created by orwant on 2011-04-07T23:59:19.000Z:
The problem occurs in the "Overview" section on http://code.google.com/apis/visualization/documentation/gallery/motionchart.html
The link in the Note for Developers section should refer to Adobe's website, since Adobe acquired Macromedia in (late) 2005.
|
1.0
|
docs refer to Macromedia website - Original [issue 573](https://code.google.com/p/google-visualization-api-issues/issues/detail?id=573) created by orwant on 2011-04-07T23:59:19.000Z:
The problem occurs in the "Overview" section on http://code.google.com/apis/visualization/documentation/gallery/motionchart.html
The link in the Note for Developers section should refer to Adobe's website, since Adobe acquired Macromedia in (late) 2005.
|
defect
|
docs refer to macromedia website original created by orwant on the problem occurs in the quot overview quot section on the link in the note for developers section should refer to adobe s website since adobe acquired macromedia in late
| 1
|
61,343
| 17,023,670,924
|
IssuesEvent
|
2021-07-03 03:12:56
|
tomhughes/trac-tickets
|
https://api.github.com/repos/tomhughes/trac-tickets
|
closed
|
Sarajevo displayed in search results as "Sarajevo, Serbia" instead of "Sarajevo, Bosnia and Herzegovina"
|
Component: nominatim Priority: minor Resolution: fixed Type: defect
|
**[Submitted to the original trac issue database at 8.50pm, Wednesday, 12th January 2011]**
steps to reproduce:
1. load http://www.openstreetmap.org/
2. type "sarajevo" in search box
3. click "Go"
4. Search Results are displayed:
--- second result is "City Sarajevo, Serbia". Expected result is "City Sarajevo, Bosnia and Herzegovina"
--- third result is "Railway Station Sarajevo... Serbia". Expected result is "Railway Station Sarajevo... Bosnia and Herzegovina"
--- fourth result is "Bus Stop Sarajevo, Grbavica, Serbia". Expected result is "Bus Stop Sarajevo, Bosnia and Herzegovina"
Please fix this. Sarajevo is capital of Bosnia and Herzegovina, it's not in Serbia.
|
1.0
|
Sarajevo displayed in search results as "Sarajevo, Serbia" instead of "Sarajevo, Bosnia and Herzegovina" - **[Submitted to the original trac issue database at 8.50pm, Wednesday, 12th January 2011]**
steps to reproduce:
1. load http://www.openstreetmap.org/
2. type "sarajevo" in search box
3. click "Go"
4. Search Results are displayed:
--- second result is "City Sarajevo, Serbia". Expected result is "City Sarajevo, Bosnia and Herzegovina"
--- third result is "Railway Station Sarajevo... Serbia". Expected result is "Railway Station Sarajevo... Bosnia and Herzegovina"
--- fourth result is "Bus Stop Sarajevo, Grbavica, Serbia". Expected result is "Bus Stop Sarajevo, Bosnia and Herzegovina"
Please fix this. Sarajevo is capital of Bosnia and Herzegovina, it's not in Serbia.
|
defect
|
sarajevo displayed in search results as sarajevo serbia instead of sarajevo bosnia and herzegovina steps to reproduce load type sarajevo in search box click go search results are displayed second result is city sarajevo serbia expected result is city sarajevo bosnia and herzegovina third result is railway station sarajevo serbia expected result is railway station sarajevo bosnia and herzegovina fourth result is bus stop sarajevo grbavica serbia expected result is bus stop sarajevo bosnia and herzegovina please fix this sarajevo is capital of bosnia and herzegovina it s not in serbia
| 1
|
157,271
| 19,957,076,916
|
IssuesEvent
|
2022-01-28 01:21:53
|
panasalap/linux-4.1.15
|
https://api.github.com/repos/panasalap/linux-4.1.15
|
opened
|
CVE-2018-16871 (High) detected in linux-yocto-4.1v4.1.17
|
security vulnerability
|
## CVE-2018-16871 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-4.1v4.1.17</b></p></summary>
<p>
<p>[no description]</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto-4.1>https://git.yoctoproject.org/git/linux-yocto-4.1</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/nfsd/nfs4proc.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in the Linux kernel's NFS implementation, all versions 3.x and all versions 4.x up to 4.20. An attacker, who is able to mount an exported NFS filesystem, is able to trigger a null pointer dereference by using an invalid NFS sequence. This can panic the machine and deny access to the NFS server. Any outstanding disk writes to the NFS server will be lost.
<p>Publish Date: 2019-07-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16871>CVE-2018-16871</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-16871">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-16871</a></p>
<p>Release Date: 2019-07-30</p>
<p>Fix Resolution: v4.20-rc3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2018-16871 (High) detected in linux-yocto-4.1v4.1.17 - ## CVE-2018-16871 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-4.1v4.1.17</b></p></summary>
<p>
<p>[no description]</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto-4.1>https://git.yoctoproject.org/git/linux-yocto-4.1</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/nfsd/nfs4proc.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in the Linux kernel's NFS implementation, all versions 3.x and all versions 4.x up to 4.20. An attacker, who is able to mount an exported NFS filesystem, is able to trigger a null pointer dereference by using an invalid NFS sequence. This can panic the machine and deny access to the NFS server. Any outstanding disk writes to the NFS server will be lost.
<p>Publish Date: 2019-07-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16871>CVE-2018-16871</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-16871">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-16871</a></p>
<p>Release Date: 2019-07-30</p>
<p>Fix Resolution: v4.20-rc3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve high detected in linux yocto cve high severity vulnerability vulnerable library linux yocto library home page a href found in base branch master vulnerable source files fs nfsd c vulnerability details a flaw was found in the linux kernel s nfs implementation all versions x and all versions x up to an attacker who is able to mount an exported nfs filesystem is able to trigger a null pointer dereference by using an invalid nfs sequence this can panic the machine and deny access to the nfs server any outstanding disk writes to the nfs server will be lost publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource
| 0
|
273,843
| 23,789,060,480
|
IssuesEvent
|
2022-09-02 12:59:17
|
IntellectualSites/FastAsyncWorldEdit
|
https://api.github.com/repos/IntellectualSites/FastAsyncWorldEdit
|
closed
|
FastAsyncWorldedit lagging the server for a permission check
|
Requires Testing
|
### Server Implementation
Paper
### Server Version
1.17.1
### Describe the bug
For some weird reasons Fawe uses a lot of % when no one is using it: https://spark.lucko.me/FmPS683ntW
Currently 250 players online
### To Reproduce
1. Have 250 players online
2. do a spark
### Expected behaviour
Fawe shouldn't use that much when no one is using FAWE
### Screenshots / Videos
https://spark.lucko.me/FmPS683ntW
### Error log (if applicable)
_No response_
### Fawe Debugpaste
https://athion.net/ISPaster/paste/view/ee8816fd99b946f19511adb29b2b99e3
### Fawe Version
2.4.4 snapshot 265
### Checklist
- [X] I have included a Fawe debugpaste.
- [X] I am using the newest build from https://ci.athion.net/job/FastAsyncWorldEdit/ and the issue still persists.
### Anything else?
_No response_
|
1.0
|
FastAsyncWorldedit lagging the server for a permission check - ### Server Implementation
Paper
### Server Version
1.17.1
### Describe the bug
For some weird reasons Fawe uses a lot of % when no one is using it: https://spark.lucko.me/FmPS683ntW
Currently 250 players online
### To Reproduce
1. Have 250 players online
2. do a spark
### Expected behaviour
Fawe shouldn't use that much when no one is using FAWE
### Screenshots / Videos
https://spark.lucko.me/FmPS683ntW
### Error log (if applicable)
_No response_
### Fawe Debugpaste
https://athion.net/ISPaster/paste/view/ee8816fd99b946f19511adb29b2b99e3
### Fawe Version
2.4.4 snapshot 265
### Checklist
- [X] I have included a Fawe debugpaste.
- [X] I am using the newest build from https://ci.athion.net/job/FastAsyncWorldEdit/ and the issue still persists.
### Anything else?
_No response_
|
non_defect
|
fastasyncworldedit lagging the server for a permission check server implementation paper server version describe the bug for some weird reasons fawe uses a lot of when no one is using it currently players online to reproduce have players online do a spark expected behaviour fawe shouldn t use that much when no one is using fawe screenshots videos error log if applicable no response fawe debugpaste fawe version snapshot checklist i have included a fawe debugpaste i am using the newest build from and the issue still persists anything else no response
| 0
|
505,323
| 14,631,479,967
|
IssuesEvent
|
2020-12-23 20:00:27
|
googleapis/java-securitycenter
|
https://api.github.com/repos/googleapis/java-securitycenter
|
closed
|
Naming conflict for SecurityMarksName
|
api: securitycenter priority: p2 type: bug
|
Capitalization of the class is different in v1beta1 and v1 which is causing conflicts:
https://github.com/googleapis/java-securitycenter/blob/master/proto-google-cloud-securitycenter-v1beta1/src/main/java/com/google/cloud/securitycenter/v1beta1/SecuritymarksName.java
https://github.com/googleapis/java-securitycenter/blob/master/proto-google-cloud-securitycenter-v1/src/main/java/com/google/cloud/securitycenter/v1/SecurityMarksName.java
|
1.0
|
Naming conflict for SecurityMarksName - Capitalization of the class is different in v1beta1 and v1 which is causing conflicts:
https://github.com/googleapis/java-securitycenter/blob/master/proto-google-cloud-securitycenter-v1beta1/src/main/java/com/google/cloud/securitycenter/v1beta1/SecuritymarksName.java
https://github.com/googleapis/java-securitycenter/blob/master/proto-google-cloud-securitycenter-v1/src/main/java/com/google/cloud/securitycenter/v1/SecurityMarksName.java
|
non_defect
|
naming conflict for securitymarksname capitalization of the class is different in and which is causing conflicts
| 0
|
504,525
| 14,620,069,618
|
IssuesEvent
|
2020-12-22 19:01:24
|
googleapis/elixir-google-api
|
https://api.github.com/repos/googleapis/elixir-google-api
|
closed
|
Synthesis failed for Apigee
|
autosynth failure priority: p1 type: bug
|
Hello! Autosynth couldn't regenerate Apigee. :broken_heart:
Here's the output from running `synth.py`:
```
e/v1/model/google_cloud_apigee_v1_resource_config.ex.
Writing GoogleCloudApigeeV1ResourceFile to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_resource_file.ex.
Writing GoogleCloudApigeeV1ResourceFiles to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_resource_files.ex.
Writing GoogleCloudApigeeV1ResourceStatus to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_resource_status.ex.
Writing GoogleCloudApigeeV1Result to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_result.ex.
Writing GoogleCloudApigeeV1RevisionStatus to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_revision_status.ex.
Writing GoogleCloudApigeeV1RoutingRule to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_routing_rule.ex.
Writing GoogleCloudApigeeV1RuntimeTraceConfig to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_runtime_trace_config.ex.
Writing GoogleCloudApigeeV1RuntimeTraceConfigOverride to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_runtime_trace_config_override.ex.
Writing GoogleCloudApigeeV1RuntimeTraceSamplingConfig to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_runtime_trace_sampling_config.ex.
Writing GoogleCloudApigeeV1Schema to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_schema.ex.
Writing GoogleCloudApigeeV1SchemaSchemaElement to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_schema_schema_element.ex.
Writing GoogleCloudApigeeV1SchemaSchemaProperty to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_schema_schema_property.ex.
Writing GoogleCloudApigeeV1ServiceIssuersMapping to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_service_issuers_mapping.ex.
Writing GoogleCloudApigeeV1Session to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_session.ex.
Writing GoogleCloudApigeeV1SharedFlow to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_shared_flow.ex.
Writing GoogleCloudApigeeV1SharedFlowRevision to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_shared_flow_revision.ex.
Writing GoogleCloudApigeeV1Stats to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_stats.ex.
Writing GoogleCloudApigeeV1StatsEnvironmentStats to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_stats_environment_stats.ex.
Writing GoogleCloudApigeeV1StatsHostStats to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_stats_host_stats.ex.
Writing GoogleCloudApigeeV1Subscription to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_subscription.ex.
Writing GoogleCloudApigeeV1SyncAuthorization to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_sync_authorization.ex.
Writing GoogleCloudApigeeV1TargetServer to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_target_server.ex.
Writing GoogleCloudApigeeV1TargetServerConfig to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_target_server_config.ex.
Writing GoogleCloudApigeeV1TestDatastoreResponse to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_test_datastore_response.ex.
Writing GoogleCloudApigeeV1TlsInfo to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_tls_info.ex.
Writing GoogleCloudApigeeV1TlsInfoCommonName to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_tls_info_common_name.ex.
Writing GoogleCloudApigeeV1TlsInfoConfig to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_tls_info_config.ex.
Writing GoogleCloudApigeeV1UpdateError to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_update_error.ex.
Writing GoogleIamV1AuditConfig to clients/apigee/lib/google_api/apigee/v1/model/google_iam_v1_audit_config.ex.
Writing GoogleIamV1AuditLogConfig to clients/apigee/lib/google_api/apigee/v1/model/google_iam_v1_audit_log_config.ex.
Writing GoogleIamV1Binding to clients/apigee/lib/google_api/apigee/v1/model/google_iam_v1_binding.ex.
Writing GoogleIamV1Policy to clients/apigee/lib/google_api/apigee/v1/model/google_iam_v1_policy.ex.
Writing GoogleIamV1SetIamPolicyRequest to clients/apigee/lib/google_api/apigee/v1/model/google_iam_v1_set_iam_policy_request.ex.
Writing GoogleIamV1TestIamPermissionsRequest to clients/apigee/lib/google_api/apigee/v1/model/google_iam_v1_test_iam_permissions_request.ex.
Writing GoogleIamV1TestIamPermissionsResponse to clients/apigee/lib/google_api/apigee/v1/model/google_iam_v1_test_iam_permissions_response.ex.
Writing GoogleLongrunningListOperationsResponse to clients/apigee/lib/google_api/apigee/v1/model/google_longrunning_list_operations_response.ex.
Writing GoogleLongrunningOperation to clients/apigee/lib/google_api/apigee/v1/model/google_longrunning_operation.ex.
Writing GoogleProtobufEmpty to clients/apigee/lib/google_api/apigee/v1/model/google_protobuf_empty.ex.
Writing GoogleRpcPreconditionFailure to clients/apigee/lib/google_api/apigee/v1/model/google_rpc_precondition_failure.ex.
Writing GoogleRpcPreconditionFailureViolation to clients/apigee/lib/google_api/apigee/v1/model/google_rpc_precondition_failure_violation.ex.
Writing GoogleRpcStatus to clients/apigee/lib/google_api/apigee/v1/model/google_rpc_status.ex.
Writing GoogleTypeExpr to clients/apigee/lib/google_api/apigee/v1/model/google_type_expr.ex.
Writing Hybrid to clients/apigee/lib/google_api/apigee/v1/api/hybrid.ex.
Writing Organizations to clients/apigee/lib/google_api/apigee/v1/api/organizations.ex.
Writing Projects to clients/apigee/lib/google_api/apigee/v1/api/projects.ex.
Writing connection.ex.
Writing metadata.ex.
Writing mix.exs
Writing README.md
Writing LICENSE
Writing .gitignore
Writing config/config.exs
Writing test/test_helper.exs
13:16:10.647 [info] Found only discovery_revision and/or formatting changes. Not significant enough for a PR.
fixing file permissions
Traceback (most recent call last):
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 193, in _run_module_as_main
"__main__", mod_spec)
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 85, in _run_code
exec(code, run_globals)
File "/tmpfs/src/github/synthtool/synthtool/__main__.py", line 102, in <module>
main()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/click/core.py", line 829, in __call__
return self.main(*args, **kwargs)
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/click/core.py", line 782, in main
rv = self.invoke(ctx)
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/click/core.py", line 1066, in invoke
return ctx.invoke(self.callback, **ctx.params)
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/click/core.py", line 610, in invoke
return callback(*args, **kwargs)
File "/tmpfs/src/github/synthtool/synthtool/__main__.py", line 94, in main
spec.loader.exec_module(synth_module) # type: ignore
File "/tmpfs/src/github/synthtool/synthtool/metadata.py", line 252, in __exit__
self.observer.stop()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/watchdog/utils/__init__.py", line 81, in stop
self.on_thread_stop()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/watchdog/observers/api.py", line 361, in on_thread_stop
self.unschedule_all()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/watchdog/observers/api.py", line 357, in unschedule_all
self._clear_emitters()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/watchdog/observers/api.py", line 231, in _clear_emitters
emitter.stop()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/watchdog/utils/__init__.py", line 81, in stop
self.on_thread_stop()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/watchdog/observers/inotify.py", line 121, in on_thread_stop
self._inotify.close()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/watchdog/observers/inotify_buffer.py", line 50, in close
self.stop()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/watchdog/utils/__init__.py", line 81, in stop
self.on_thread_stop()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/watchdog/observers/inotify_buffer.py", line 46, in on_thread_stop
self._inotify.close()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/watchdog/observers/inotify_c.py", line 277, in close
os.close(self._inotify_fd)
OSError: [Errno 9] Bad file descriptor
2020-12-18 05:16:13,715 autosynth [ERROR] > Synthesis failed
2020-12-18 05:16:13,715 autosynth [DEBUG] > Running: git clean -fdx
Removing __pycache__/
Traceback (most recent call last):
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 193, in _run_module_as_main
"__main__", mod_spec)
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 85, in _run_code
exec(code, run_globals)
File "/tmpfs/src/github/synthtool/autosynth/synth.py", line 354, in <module>
main()
File "/tmpfs/src/github/synthtool/autosynth/synth.py", line 189, in main
return _inner_main(temp_dir)
File "/tmpfs/src/github/synthtool/autosynth/synth.py", line 291, in _inner_main
).synthesize(synth_log_path / "sponge_log.log")
File "/tmpfs/src/github/synthtool/autosynth/synthesizer.py", line 120, in synthesize
synth_proc.check_returncode() # Raise an exception.
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/subprocess.py", line 389, in check_returncode
self.stderr)
subprocess.CalledProcessError: Command '['/tmpfs/src/github/synthtool/env/bin/python3', '-m', 'synthtool', '--metadata', 'clients/apigee/synth.metadata', 'synth.py', '--', 'Apigee']' returned non-zero exit status 1.
```
Google internal developers can see the full log [here](http://sponge2/results/invocations/3a455424-7540-46a9-bb77-8265c8f04c06/targets/github%2Fsynthtool;config=default/tests;query=elixir-google-api;failed=false).
|
1.0
|
Synthesis failed for Apigee - Hello! Autosynth couldn't regenerate Apigee. :broken_heart:
Here's the output from running `synth.py`:
```
e/v1/model/google_cloud_apigee_v1_resource_config.ex.
Writing GoogleCloudApigeeV1ResourceFile to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_resource_file.ex.
Writing GoogleCloudApigeeV1ResourceFiles to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_resource_files.ex.
Writing GoogleCloudApigeeV1ResourceStatus to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_resource_status.ex.
Writing GoogleCloudApigeeV1Result to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_result.ex.
Writing GoogleCloudApigeeV1RevisionStatus to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_revision_status.ex.
Writing GoogleCloudApigeeV1RoutingRule to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_routing_rule.ex.
Writing GoogleCloudApigeeV1RuntimeTraceConfig to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_runtime_trace_config.ex.
Writing GoogleCloudApigeeV1RuntimeTraceConfigOverride to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_runtime_trace_config_override.ex.
Writing GoogleCloudApigeeV1RuntimeTraceSamplingConfig to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_runtime_trace_sampling_config.ex.
Writing GoogleCloudApigeeV1Schema to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_schema.ex.
Writing GoogleCloudApigeeV1SchemaSchemaElement to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_schema_schema_element.ex.
Writing GoogleCloudApigeeV1SchemaSchemaProperty to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_schema_schema_property.ex.
Writing GoogleCloudApigeeV1ServiceIssuersMapping to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_service_issuers_mapping.ex.
Writing GoogleCloudApigeeV1Session to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_session.ex.
Writing GoogleCloudApigeeV1SharedFlow to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_shared_flow.ex.
Writing GoogleCloudApigeeV1SharedFlowRevision to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_shared_flow_revision.ex.
Writing GoogleCloudApigeeV1Stats to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_stats.ex.
Writing GoogleCloudApigeeV1StatsEnvironmentStats to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_stats_environment_stats.ex.
Writing GoogleCloudApigeeV1StatsHostStats to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_stats_host_stats.ex.
Writing GoogleCloudApigeeV1Subscription to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_subscription.ex.
Writing GoogleCloudApigeeV1SyncAuthorization to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_sync_authorization.ex.
Writing GoogleCloudApigeeV1TargetServer to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_target_server.ex.
Writing GoogleCloudApigeeV1TargetServerConfig to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_target_server_config.ex.
Writing GoogleCloudApigeeV1TestDatastoreResponse to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_test_datastore_response.ex.
Writing GoogleCloudApigeeV1TlsInfo to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_tls_info.ex.
Writing GoogleCloudApigeeV1TlsInfoCommonName to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_tls_info_common_name.ex.
Writing GoogleCloudApigeeV1TlsInfoConfig to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_tls_info_config.ex.
Writing GoogleCloudApigeeV1UpdateError to clients/apigee/lib/google_api/apigee/v1/model/google_cloud_apigee_v1_update_error.ex.
Writing GoogleIamV1AuditConfig to clients/apigee/lib/google_api/apigee/v1/model/google_iam_v1_audit_config.ex.
Writing GoogleIamV1AuditLogConfig to clients/apigee/lib/google_api/apigee/v1/model/google_iam_v1_audit_log_config.ex.
Writing GoogleIamV1Binding to clients/apigee/lib/google_api/apigee/v1/model/google_iam_v1_binding.ex.
Writing GoogleIamV1Policy to clients/apigee/lib/google_api/apigee/v1/model/google_iam_v1_policy.ex.
Writing GoogleIamV1SetIamPolicyRequest to clients/apigee/lib/google_api/apigee/v1/model/google_iam_v1_set_iam_policy_request.ex.
Writing GoogleIamV1TestIamPermissionsRequest to clients/apigee/lib/google_api/apigee/v1/model/google_iam_v1_test_iam_permissions_request.ex.
Writing GoogleIamV1TestIamPermissionsResponse to clients/apigee/lib/google_api/apigee/v1/model/google_iam_v1_test_iam_permissions_response.ex.
Writing GoogleLongrunningListOperationsResponse to clients/apigee/lib/google_api/apigee/v1/model/google_longrunning_list_operations_response.ex.
Writing GoogleLongrunningOperation to clients/apigee/lib/google_api/apigee/v1/model/google_longrunning_operation.ex.
Writing GoogleProtobufEmpty to clients/apigee/lib/google_api/apigee/v1/model/google_protobuf_empty.ex.
Writing GoogleRpcPreconditionFailure to clients/apigee/lib/google_api/apigee/v1/model/google_rpc_precondition_failure.ex.
Writing GoogleRpcPreconditionFailureViolation to clients/apigee/lib/google_api/apigee/v1/model/google_rpc_precondition_failure_violation.ex.
Writing GoogleRpcStatus to clients/apigee/lib/google_api/apigee/v1/model/google_rpc_status.ex.
Writing GoogleTypeExpr to clients/apigee/lib/google_api/apigee/v1/model/google_type_expr.ex.
Writing Hybrid to clients/apigee/lib/google_api/apigee/v1/api/hybrid.ex.
Writing Organizations to clients/apigee/lib/google_api/apigee/v1/api/organizations.ex.
Writing Projects to clients/apigee/lib/google_api/apigee/v1/api/projects.ex.
Writing connection.ex.
Writing metadata.ex.
Writing mix.exs
Writing README.md
Writing LICENSE
Writing .gitignore
Writing config/config.exs
Writing test/test_helper.exs
13:16:10.647 [info] Found only discovery_revision and/or formatting changes. Not significant enough for a PR.
fixing file permissions
Traceback (most recent call last):
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 193, in _run_module_as_main
"__main__", mod_spec)
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 85, in _run_code
exec(code, run_globals)
File "/tmpfs/src/github/synthtool/synthtool/__main__.py", line 102, in <module>
main()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/click/core.py", line 829, in __call__
return self.main(*args, **kwargs)
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/click/core.py", line 782, in main
rv = self.invoke(ctx)
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/click/core.py", line 1066, in invoke
return ctx.invoke(self.callback, **ctx.params)
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/click/core.py", line 610, in invoke
return callback(*args, **kwargs)
File "/tmpfs/src/github/synthtool/synthtool/__main__.py", line 94, in main
spec.loader.exec_module(synth_module) # type: ignore
File "/tmpfs/src/github/synthtool/synthtool/metadata.py", line 252, in __exit__
self.observer.stop()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/watchdog/utils/__init__.py", line 81, in stop
self.on_thread_stop()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/watchdog/observers/api.py", line 361, in on_thread_stop
self.unschedule_all()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/watchdog/observers/api.py", line 357, in unschedule_all
self._clear_emitters()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/watchdog/observers/api.py", line 231, in _clear_emitters
emitter.stop()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/watchdog/utils/__init__.py", line 81, in stop
self.on_thread_stop()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/watchdog/observers/inotify.py", line 121, in on_thread_stop
self._inotify.close()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/watchdog/observers/inotify_buffer.py", line 50, in close
self.stop()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/watchdog/utils/__init__.py", line 81, in stop
self.on_thread_stop()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/watchdog/observers/inotify_buffer.py", line 46, in on_thread_stop
self._inotify.close()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/watchdog/observers/inotify_c.py", line 277, in close
os.close(self._inotify_fd)
OSError: [Errno 9] Bad file descriptor
2020-12-18 05:16:13,715 autosynth [ERROR] > Synthesis failed
2020-12-18 05:16:13,715 autosynth [DEBUG] > Running: git clean -fdx
Removing __pycache__/
Traceback (most recent call last):
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 193, in _run_module_as_main
"__main__", mod_spec)
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 85, in _run_code
exec(code, run_globals)
File "/tmpfs/src/github/synthtool/autosynth/synth.py", line 354, in <module>
main()
File "/tmpfs/src/github/synthtool/autosynth/synth.py", line 189, in main
return _inner_main(temp_dir)
File "/tmpfs/src/github/synthtool/autosynth/synth.py", line 291, in _inner_main
).synthesize(synth_log_path / "sponge_log.log")
File "/tmpfs/src/github/synthtool/autosynth/synthesizer.py", line 120, in synthesize
synth_proc.check_returncode() # Raise an exception.
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/subprocess.py", line 389, in check_returncode
self.stderr)
subprocess.CalledProcessError: Command '['/tmpfs/src/github/synthtool/env/bin/python3', '-m', 'synthtool', '--metadata', 'clients/apigee/synth.metadata', 'synth.py', '--', 'Apigee']' returned non-zero exit status 1.
```
Google internal developers can see the full log [here](http://sponge2/results/invocations/3a455424-7540-46a9-bb77-8265c8f04c06/targets/github%2Fsynthtool;config=default/tests;query=elixir-google-api;failed=false).
|
non_defect
|
synthesis failed for apigee hello autosynth couldn t regenerate apigee broken heart here s the output from running synth py e model google cloud apigee resource config ex writing to clients apigee lib google api apigee model google cloud apigee resource file ex writing to clients apigee lib google api apigee model google cloud apigee resource files ex writing to clients apigee lib google api apigee model google cloud apigee resource status ex writing to clients apigee lib google api apigee model google cloud apigee result ex writing to clients apigee lib google api apigee model google cloud apigee revision status ex writing to clients apigee lib google api apigee model google cloud apigee routing rule ex writing to clients apigee lib google api apigee model google cloud apigee runtime trace config ex writing to clients apigee lib google api apigee model google cloud apigee runtime trace config override ex writing to clients apigee lib google api apigee model google cloud apigee runtime trace sampling config ex writing to clients apigee lib google api apigee model google cloud apigee schema ex writing to clients apigee lib google api apigee model google cloud apigee schema schema element ex writing to clients apigee lib google api apigee model google cloud apigee schema schema property ex writing to clients apigee lib google api apigee model google cloud apigee service issuers mapping ex writing to clients apigee lib google api apigee model google cloud apigee session ex writing to clients apigee lib google api apigee model google cloud apigee shared flow ex writing to clients apigee lib google api apigee model google cloud apigee shared flow revision ex writing to clients apigee lib google api apigee model google cloud apigee stats ex writing to clients apigee lib google api apigee model google cloud apigee stats environment stats ex writing to clients apigee lib google api apigee model google cloud apigee stats host stats ex writing to clients apigee lib google api apigee model google cloud apigee subscription ex writing to clients apigee lib google api apigee model google cloud apigee sync authorization ex writing to clients apigee lib google api apigee model google cloud apigee target server ex writing to clients apigee lib google api apigee model google cloud apigee target server config ex writing to clients apigee lib google api apigee model google cloud apigee test datastore response ex writing to clients apigee lib google api apigee model google cloud apigee tls info ex writing to clients apigee lib google api apigee model google cloud apigee tls info common name ex writing to clients apigee lib google api apigee model google cloud apigee tls info config ex writing to clients apigee lib google api apigee model google cloud apigee update error ex writing to clients apigee lib google api apigee model google iam audit config ex writing to clients apigee lib google api apigee model google iam audit log config ex writing to clients apigee lib google api apigee model google iam binding ex writing to clients apigee lib google api apigee model google iam policy ex writing to clients apigee lib google api apigee model google iam set iam policy request ex writing to clients apigee lib google api apigee model google iam test iam permissions request ex writing to clients apigee lib google api apigee model google iam test iam permissions response ex writing googlelongrunninglistoperationsresponse to clients apigee lib google api apigee model google longrunning list operations response ex writing googlelongrunningoperation to clients apigee lib google api apigee model google longrunning operation ex writing googleprotobufempty to clients apigee lib google api apigee model google protobuf empty ex writing googlerpcpreconditionfailure to clients apigee lib google api apigee model google rpc precondition failure ex writing googlerpcpreconditionfailureviolation to clients apigee lib google api apigee model google rpc precondition failure violation ex writing googlerpcstatus to clients apigee lib google api apigee model google rpc status ex writing googletypeexpr to clients apigee lib google api apigee model google type expr ex writing hybrid to clients apigee lib google api apigee api hybrid ex writing organizations to clients apigee lib google api apigee api organizations ex writing projects to clients apigee lib google api apigee api projects ex writing connection ex writing metadata ex writing mix exs writing readme md writing license writing gitignore writing config config exs writing test test helper exs found only discovery revision and or formatting changes not significant enough for a pr fixing file permissions traceback most recent call last file home kbuilder pyenv versions lib runpy py line in run module as main main mod spec file home kbuilder pyenv versions lib runpy py line in run code exec code run globals file tmpfs src github synthtool synthtool main py line in main file tmpfs src github synthtool env lib site packages click core py line in call return self main args kwargs file tmpfs src github synthtool env lib site packages click core py line in main rv self invoke ctx file tmpfs src github synthtool env lib site packages click core py line in invoke return ctx invoke self callback ctx params file tmpfs src github synthtool env lib site packages click core py line in invoke return callback args kwargs file tmpfs src github synthtool synthtool main py line in main spec loader exec module synth module type ignore file tmpfs src github synthtool synthtool metadata py line in exit self observer stop file tmpfs src github synthtool env lib site packages watchdog utils init py line in stop self on thread stop file tmpfs src github synthtool env lib site packages watchdog observers api py line in on thread stop self unschedule all file tmpfs src github synthtool env lib site packages watchdog observers api py line in unschedule all self clear emitters file tmpfs src github synthtool env lib site packages watchdog observers api py line in clear emitters emitter stop file tmpfs src github synthtool env lib site packages watchdog utils init py line in stop self on thread stop file tmpfs src github synthtool env lib site packages watchdog observers inotify py line in on thread stop self inotify close file tmpfs src github synthtool env lib site packages watchdog observers inotify buffer py line in close self stop file tmpfs src github synthtool env lib site packages watchdog utils init py line in stop self on thread stop file tmpfs src github synthtool env lib site packages watchdog observers inotify buffer py line in on thread stop self inotify close file tmpfs src github synthtool env lib site packages watchdog observers inotify c py line in close os close self inotify fd oserror bad file descriptor autosynth synthesis failed autosynth running git clean fdx removing pycache traceback most recent call last file home kbuilder pyenv versions lib runpy py line in run module as main main mod spec file home kbuilder pyenv versions lib runpy py line in run code exec code run globals file tmpfs src github synthtool autosynth synth py line in main file tmpfs src github synthtool autosynth synth py line in main return inner main temp dir file tmpfs src github synthtool autosynth synth py line in inner main synthesize synth log path sponge log log file tmpfs src github synthtool autosynth synthesizer py line in synthesize synth proc check returncode raise an exception file home kbuilder pyenv versions lib subprocess py line in check returncode self stderr subprocess calledprocesserror command returned non zero exit status google internal developers can see the full log
| 0
|
68,657
| 21,778,400,538
|
IssuesEvent
|
2022-05-13 15:57:58
|
networkx/networkx
|
https://api.github.com/repos/networkx/networkx
|
closed
|
Defects of Bridges Algorithms
|
Defect
|
Algorithms in the [Bridges](https://networkx.org/documentation/stable/reference/algorithms/bridges.html) section only applicable for undirected graphs. However, this is not stated in the documentation. They `Raise` `NetworkXNotImplemented` when the input is a directed graph. However, I am a bit confused about the following point:
Output of `nx.bridges(G)` is `<generator object bridges at 0x7f70733bb050>` . So, it seems that it works for directed graphs as well.
However, `list(nx.bridges(G))` raises `NetworkXNotImplemented`.
Is this expected? Should not `nx.bridges(G)` directly raise `NetworkXNotImplemented` instead?
With your guidance I am willing to work on this issue.
@rossbar @MridulS @dschult
|
1.0
|
Defects of Bridges Algorithms - Algorithms in the [Bridges](https://networkx.org/documentation/stable/reference/algorithms/bridges.html) section only applicable for undirected graphs. However, this is not stated in the documentation. They `Raise` `NetworkXNotImplemented` when the input is a directed graph. However, I am a bit confused about the following point:
Output of `nx.bridges(G)` is `<generator object bridges at 0x7f70733bb050>` . So, it seems that it works for directed graphs as well.
However, `list(nx.bridges(G))` raises `NetworkXNotImplemented`.
Is this expected? Should not `nx.bridges(G)` directly raise `NetworkXNotImplemented` instead?
With your guidance I am willing to work on this issue.
@rossbar @MridulS @dschult
|
defect
|
defects of bridges algorithms algorithms in the section only applicable for undirected graphs however this is not stated in the documentation they raise networkxnotimplemented when the input is a directed graph however i am a bit confused about the following point output of nx bridges g is so it seems that it works for directed graphs as well however list nx bridges g raises networkxnotimplemented is this expected should not nx bridges g directly raise networkxnotimplemented instead with your guidance i am willing to work on this issue rossbar mriduls dschult
| 1
|
18,994
| 3,120,785,607
|
IssuesEvent
|
2015-09-05 02:02:03
|
framingeinstein/issues-test
|
https://api.github.com/repos/framingeinstein/issues-test
|
closed
|
SRP-54: Search Rolled Out Incorrectly
|
priority:critical resolution:fixed type:defect
|
Search as it was displayed in beta for 1.1 was NOT supposed to be rolled out as is as B2C product and pricing is shown in B2B.
|
1.0
|
SRP-54: Search Rolled Out Incorrectly - Search as it was displayed in beta for 1.1 was NOT supposed to be rolled out as is as B2C product and pricing is shown in B2B.
|
defect
|
srp search rolled out incorrectly search as it was displayed in beta for was not supposed to be rolled out as is as product and pricing is shown in
| 1
|
15,173
| 2,850,245,739
|
IssuesEvent
|
2015-05-31 12:04:24
|
damonkohler/android-scripting
|
https://api.github.com/repos/damonkohler/android-scripting
|
closed
|
webView does not open properly
|
auto-migrated Priority-Medium Type-Defect
|
```
What device(s) are you experiencing the problem on?
galaxy note 8.0
What firmware version are you running on the device?
android 4.1.2
What steps will reproduce the problem?
1.refer to issue # 479. the steps are virtually the same
2. code can be found here:
http://stackoverflow.com/questions/7154669/send-events-from-python-to-javascript
-using-sl4a
What is the expected output? What do you see instead?
supposedly a html page will load. all I get is a blank screen
What version of the product are you using? On what operating system?
sl4a r6. py4a r6
Please provide any additional information below.
tried giving the url value in the webVIewShow a non existent location. still
ends up with a white screen
```
Original issue reported on code.google.com by `strike6...@yahoo.com.ph` on 25 Aug 2013 at 8:22
|
1.0
|
webView does not open properly - ```
What device(s) are you experiencing the problem on?
galaxy note 8.0
What firmware version are you running on the device?
android 4.1.2
What steps will reproduce the problem?
1.refer to issue # 479. the steps are virtually the same
2. code can be found here:
http://stackoverflow.com/questions/7154669/send-events-from-python-to-javascript
-using-sl4a
What is the expected output? What do you see instead?
supposedly a html page will load. all I get is a blank screen
What version of the product are you using? On what operating system?
sl4a r6. py4a r6
Please provide any additional information below.
tried giving the url value in the webVIewShow a non existent location. still
ends up with a white screen
```
Original issue reported on code.google.com by `strike6...@yahoo.com.ph` on 25 Aug 2013 at 8:22
|
defect
|
webview does not open properly what device s are you experiencing the problem on galaxy note what firmware version are you running on the device android what steps will reproduce the problem refer to issue the steps are virtually the same code can be found here using what is the expected output what do you see instead supposedly a html page will load all i get is a blank screen what version of the product are you using on what operating system please provide any additional information below tried giving the url value in the webviewshow a non existent location still ends up with a white screen original issue reported on code google com by yahoo com ph on aug at
| 1
|
4,090
| 2,610,087,244
|
IssuesEvent
|
2015-02-26 18:26:30
|
chrsmith/dsdsdaadf
|
https://api.github.com/repos/chrsmith/dsdsdaadf
|
opened
|
深圳痤疮多少钱
|
auto-migrated Priority-Medium Type-Defect
|
```
深圳痤疮多少钱【深圳韩方科颜全国热线400-869-1818,24小时QQ4
008691818】深圳韩方科颜专业祛痘连锁机构,机构以韩国秘方��
�—韩方科颜这一国妆准字号治疗型权威,祛痘佳品,韩方科�
��专业祛痘连锁机构,采用韩国秘方配合专业“不反弹”健康
祛痘技术并结合先进“先进豪华彩光”仪,开创国内专业治��
�粉刺、痤疮签约包治先河,成功消除了许多顾客脸上的痘痘�
��
```
-----
Original issue reported on code.google.com by `szft...@163.com` on 14 May 2014 at 7:18
|
1.0
|
深圳痤疮多少钱 - ```
深圳痤疮多少钱【深圳韩方科颜全国热线400-869-1818,24小时QQ4
008691818】深圳韩方科颜专业祛痘连锁机构,机构以韩国秘方��
�—韩方科颜这一国妆准字号治疗型权威,祛痘佳品,韩方科�
��专业祛痘连锁机构,采用韩国秘方配合专业“不反弹”健康
祛痘技术并结合先进“先进豪华彩光”仪,开创国内专业治��
�粉刺、痤疮签约包治先河,成功消除了许多顾客脸上的痘痘�
��
```
-----
Original issue reported on code.google.com by `szft...@163.com` on 14 May 2014 at 7:18
|
defect
|
深圳痤疮多少钱 深圳痤疮多少钱【 , 】深圳韩方科颜专业祛痘连锁机构,机构以韩国秘方�� �—韩方科颜这一国妆准字号治疗型权威,祛痘佳品,韩方科� ��专业祛痘连锁机构,采用韩国秘方配合专业“不反弹”健康 祛痘技术并结合先进“先进豪华彩光”仪,开创国内专业治�� �粉刺、痤疮签约包治先河,成功消除了许多顾客脸上的痘痘� �� original issue reported on code google com by szft com on may at
| 1
|
77,720
| 27,128,706,138
|
IssuesEvent
|
2023-02-16 08:08:24
|
jOOQ/jOOQ
|
https://api.github.com/repos/jOOQ/jOOQ
|
closed
|
LoggerListener::fetchEnd should check if DEBUG logging is enabled
|
T: Defect C: Functionality P: Medium E: All Editions
|
The `LoggerListener` has methods like these:
```java
public void fetchEnd(ExecuteContext ctx) {
Result<Record> buffer = (Result<Record>) ctx.data(BUFFER);
if (buffer != null && !buffer.isEmpty()) {
log(ctx.configuration(), buffer);
log.debug("Fetched row(s)", buffer.size() + (buffer.size() < maxRows() ? "" : " (or more)"));
}
}
private void log(Configuration configuration, Result<?> result) {
logMultiline("Fetched result", result.format(configuration.formattingProvider().txtFormat().maxRows(maxRows()).maxColWidth(maxColWidth())), Level.FINE);
}
private void logMultiline(String comment, String message, Level level) {
for (String line : message.split("\n")) {
if (level == Level.FINE) {
log.debug(comment, line);
}
else {
log.trace(comment, line);
}
comment = "";
}
}
```
As can be seen, there's quite some unnecessary apparent overhead that is implemented irrespective of whether logging is enabled.
There's already a global guard in `ExecuteListeners`:
```java
if (!FALSE.equals(ctx.settings().isExecuteLogging())) {
// [#6747] Avoid allocating the listener (and by consequence, the ExecuteListeners) if
// we do not DEBUG log anyway.
if (LOGGER_LISTENER_LOGGER.isDebugEnabled())
(list = init(list)).add(new LoggerListener());
}
```
Which was implemented in jOOQ 3.11: https://github.com/jOOQ/jOOQ/issues/6747. But users can attach the `LoggerListener` manually, and then they'll get all this overhead again.
|
1.0
|
LoggerListener::fetchEnd should check if DEBUG logging is enabled - The `LoggerListener` has methods like these:
```java
public void fetchEnd(ExecuteContext ctx) {
Result<Record> buffer = (Result<Record>) ctx.data(BUFFER);
if (buffer != null && !buffer.isEmpty()) {
log(ctx.configuration(), buffer);
log.debug("Fetched row(s)", buffer.size() + (buffer.size() < maxRows() ? "" : " (or more)"));
}
}
private void log(Configuration configuration, Result<?> result) {
logMultiline("Fetched result", result.format(configuration.formattingProvider().txtFormat().maxRows(maxRows()).maxColWidth(maxColWidth())), Level.FINE);
}
private void logMultiline(String comment, String message, Level level) {
for (String line : message.split("\n")) {
if (level == Level.FINE) {
log.debug(comment, line);
}
else {
log.trace(comment, line);
}
comment = "";
}
}
```
As can be seen, there's quite some unnecessary apparent overhead that is implemented irrespective of whether logging is enabled.
There's already a global guard in `ExecuteListeners`:
```java
if (!FALSE.equals(ctx.settings().isExecuteLogging())) {
// [#6747] Avoid allocating the listener (and by consequence, the ExecuteListeners) if
// we do not DEBUG log anyway.
if (LOGGER_LISTENER_LOGGER.isDebugEnabled())
(list = init(list)).add(new LoggerListener());
}
```
Which was implemented in jOOQ 3.11: https://github.com/jOOQ/jOOQ/issues/6747. But users can attach the `LoggerListener` manually, and then they'll get all this overhead again.
|
defect
|
loggerlistener fetchend should check if debug logging is enabled the loggerlistener has methods like these java public void fetchend executecontext ctx result buffer result ctx data buffer if buffer null buffer isempty log ctx configuration buffer log debug fetched row s buffer size buffer size maxrows or more private void log configuration configuration result result logmultiline fetched result result format configuration formattingprovider txtformat maxrows maxrows maxcolwidth maxcolwidth level fine private void logmultiline string comment string message level level for string line message split n if level level fine log debug comment line else log trace comment line comment as can be seen there s quite some unnecessary apparent overhead that is implemented irrespective of whether logging is enabled there s already a global guard in executelisteners java if false equals ctx settings isexecutelogging avoid allocating the listener and by consequence the executelisteners if we do not debug log anyway if logger listener logger isdebugenabled list init list add new loggerlistener which was implemented in jooq but users can attach the loggerlistener manually and then they ll get all this overhead again
| 1
|
57,125
| 15,702,992,611
|
IssuesEvent
|
2021-03-26 13:20:50
|
STEllAR-GROUP/hpx
|
https://api.github.com/repos/STEllAR-GROUP/hpx
|
closed
|
Allow triggering the output of OS thread affinity from configuration settings
|
category: init type: defect
|
When initializing HPX solely via `hpx::init_params.cfg` it seems to not be possible to trigger certain functionality such as printing the OS thread affinity information. I found no way to pass the equivalent of the command line switch `--hpx:print-bind` using the configuration object, am I missing something here?
## Specifications
- HPX Version: 1.6.0
- Platform (compiler, OS): GCC 10.2.0, Linux
|
1.0
|
Allow triggering the output of OS thread affinity from configuration settings - When initializing HPX solely via `hpx::init_params.cfg` it seems to not be possible to trigger certain functionality such as printing the OS thread affinity information. I found no way to pass the equivalent of the command line switch `--hpx:print-bind` using the configuration object, am I missing something here?
## Specifications
- HPX Version: 1.6.0
- Platform (compiler, OS): GCC 10.2.0, Linux
|
defect
|
allow triggering the output of os thread affinity from configuration settings when initializing hpx solely via hpx init params cfg it seems to not be possible to trigger certain functionality such as printing the os thread affinity information i found no way to pass the equivalent of the command line switch hpx print bind using the configuration object am i missing something here specifications hpx version platform compiler os gcc linux
| 1
|
249,068
| 7,953,650,695
|
IssuesEvent
|
2018-07-12 02:55:37
|
SpongePowered/Ore
|
https://api.github.com/repos/SpongePowered/Ore
|
closed
|
Log DB/File Actions
|
priority: high
|
Admin/mod actions should be logged. A global page for all actions and a per-user page seems like the best idea.
cc @progwml6
|
1.0
|
Log DB/File Actions - Admin/mod actions should be logged. A global page for all actions and a per-user page seems like the best idea.
cc @progwml6
|
non_defect
|
log db file actions admin mod actions should be logged a global page for all actions and a per user page seems like the best idea cc
| 0
|
810,640
| 30,251,971,324
|
IssuesEvent
|
2023-07-06 21:24:58
|
Azure/azure-sdk-tools
|
https://api.github.com/repos/Azure/azure-sdk-tools
|
closed
|
[Python APIView] Update --source-url to use ExternalLinkType
|
APIView APIView Priority 2 Python
|
https://github.com/Azure/azure-sdk-tools/pull/4296
Now we can display a clickable link instead of just text.
|
1.0
|
[Python APIView] Update --source-url to use ExternalLinkType - https://github.com/Azure/azure-sdk-tools/pull/4296
Now we can display a clickable link instead of just text.
|
non_defect
|
update source url to use externallinktype now we can display a clickable link instead of just text
| 0
|
55,727
| 30,914,158,415
|
IssuesEvent
|
2023-08-05 04:09:42
|
broomsday/volumizer
|
https://api.github.com/repos/broomsday/volumizer
|
opened
|
Include C speedup in the pip installable package not just in repo
|
performance
|
- [ ] Add C versions of functions to the package
|
True
|
Include C speedup in the pip installable package not just in repo - - [ ] Add C versions of functions to the package
|
non_defect
|
include c speedup in the pip installable package not just in repo add c versions of functions to the package
| 0
|
81,939
| 31,822,905,858
|
IssuesEvent
|
2023-09-14 04:51:16
|
SeleniumHQ/selenium
|
https://api.github.com/repos/SeleniumHQ/selenium
|
opened
|
[🐛 Bug]: Headless mode is not working properly after google chrome update.
|
I-defect needs-triaging
|
### What happened?
Headless mode is not working properly after google chrome update.
is.Displayed() and click() command is not working after google update python selenium. Please Solve it .
### How can we reproduce the issue?
```shell
You need to update selenium.
```
### Relevant log output
```shell
Error
```
### Operating System
Windows 10
### Selenium version
Python 4.12.0 (August 31, 2023)
### What are the browser(s) and version(s) where you see this issue?
Version 117.0.5938.63 (Official Build) (64-bit)
### What are the browser driver(s) and version(s) where you see this issue?
117.0.5938.62
### Are you using Selenium Grid?
_No response_
|
1.0
|
[🐛 Bug]: Headless mode is not working properly after google chrome update. - ### What happened?
Headless mode is not working properly after google chrome update.
is.Displayed() and click() command is not working after google update python selenium. Please Solve it .
### How can we reproduce the issue?
```shell
You need to update selenium.
```
### Relevant log output
```shell
Error
```
### Operating System
Windows 10
### Selenium version
Python 4.12.0 (August 31, 2023)
### What are the browser(s) and version(s) where you see this issue?
Version 117.0.5938.63 (Official Build) (64-bit)
### What are the browser driver(s) and version(s) where you see this issue?
117.0.5938.62
### Are you using Selenium Grid?
_No response_
|
defect
|
headless mode is not working properly after google chrome update what happened headless mode is not working properly after google chrome update is displayed and click command is not working after google update python selenium please solve it how can we reproduce the issue shell you need to update selenium relevant log output shell error operating system windows selenium version python august what are the browser s and version s where you see this issue version official build bit what are the browser driver s and version s where you see this issue are you using selenium grid no response
| 1
|
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.