Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 4 112 | repo_url stringlengths 33 141 | action stringclasses 3 values | title stringlengths 1 957 | labels stringlengths 4 1.11k | body stringlengths 1 261k | index stringclasses 11 values | text_combine stringlengths 95 261k | label stringclasses 2 values | text stringlengths 96 250k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
69,593 | 8,434,976,774 | IssuesEvent | 2018-10-17 11:52:33 | Altinn/altinn-studio | https://api.github.com/repos/Altinn/altinn-studio | opened | Dynamics: edit dynamics | designer logic & rules needs sketches needs spesification | **Functional architect/designer:** @-mention
**Technical architect:** @-mention
Description
As a service developer I need to be able edit already existing dynamics.
Editing dynamics should be possible both through GUI and code.
Sketch (if relevant)
(Screenshot and link to Figma, make sure your sketch is public!)
//needs scetch
**Navigation from/to (if relevant)**
This functionality is reached from...
**Technical considerations**
Input (beyond tasks) on how the user story should be solved can be put here.
**Acceptance criterea**
- What is allowed/not allowed
- Validations
- Error messages and warnings
- ...
**Tasks**
- [ ] Example task
| 1.0 | Dynamics: edit dynamics - **Functional architect/designer:** @-mention
**Technical architect:** @-mention
Description
As a service developer I need to be able edit already existing dynamics.
Editing dynamics should be possible both through GUI and code.
Sketch (if relevant)
(Screenshot and link to Figma, make sure your sketch is public!)
//needs scetch
**Navigation from/to (if relevant)**
This functionality is reached from...
**Technical considerations**
Input (beyond tasks) on how the user story should be solved can be put here.
**Acceptance criterea**
- What is allowed/not allowed
- Validations
- Error messages and warnings
- ...
**Tasks**
- [ ] Example task
| design | dynamics edit dynamics functional architect designer mention technical architect mention description as a service developer i need to be able edit already existing dynamics editing dynamics should be possible both through gui and code sketch if relevant screenshot and link to figma make sure your sketch is public needs scetch navigation from to if relevant this functionality is reached from technical considerations input beyond tasks on how the user story should be solved can be put here acceptance criterea what is allowed not allowed validations error messages and warnings tasks example task | 1 |
426,578 | 12,374,404,576 | IssuesEvent | 2020-05-19 01:28:35 | Matteas-Eden/roll-for-reaction | https://api.github.com/repos/Matteas-Eden/roll-for-reaction | closed | Bow sprite not found crashes game | High Priority bug | **Bug Summary**
Due to a missing `bow.png` file, the game fails to compile and cannot be played.
**Test Case(s)**
<!-- List the relevant unsuccessful test case(s) -->
---
**Expected behavior**
The game compiles.
**Observed Behaviour**
The game does not compile.
**Steps To Reproduce**
<!-- The steps performed to reproduce the bug -->
1. Checkout `master`
2. Run `yarn start`
3. Observe
**Environment**
- Version: cf1e9ae
- OS: Arch Linux
- Browser:
---
**Code Examples**
**Stack Trace**
**Screenshots**
**Error Report**
---
**Additional context**
<!-- Add any other context about the problem here -->
| 1.0 | Bow sprite not found crashes game - **Bug Summary**
Due to a missing `bow.png` file, the game fails to compile and cannot be played.
**Test Case(s)**
<!-- List the relevant unsuccessful test case(s) -->
---
**Expected behavior**
The game compiles.
**Observed Behaviour**
The game does not compile.
**Steps To Reproduce**
<!-- The steps performed to reproduce the bug -->
1. Checkout `master`
2. Run `yarn start`
3. Observe
**Environment**
- Version: cf1e9ae
- OS: Arch Linux
- Browser:
---
**Code Examples**
**Stack Trace**
**Screenshots**
**Error Report**
---
**Additional context**
<!-- Add any other context about the problem here -->
| non_design | bow sprite not found crashes game bug summary due to a missing bow png file the game fails to compile and cannot be played test case s expected behavior the game compiles observed behaviour the game does not compile steps to reproduce checkout master run yarn start observe environment version os arch linux browser code examples stack trace screenshots error report additional context | 0 |
285,314 | 8,757,203,537 | IssuesEvent | 2018-12-14 20:22:43 | richelbilderbeek/djog_unos_2018 | https://api.github.com/repos/richelbilderbeek/djog_unos_2018 | opened | Agent has stamina | low priority | I would like the agents to have stamina, so when the agents are swimming for too long, they drown. | 1.0 | Agent has stamina - I would like the agents to have stamina, so when the agents are swimming for too long, they drown. | non_design | agent has stamina i would like the agents to have stamina so when the agents are swimming for too long they drown | 0 |
86,341 | 3,710,830,203 | IssuesEvent | 2016-03-02 07:17:45 | elementary/icons | https://api.github.com/repos/elementary/icons | closed | Differentiate between code mimes by color | Priority: Wishlist Status: Confirmed | In a folder full of HTML, PHP, JS and CSS files, it is difficult to differentiate between them quickly by color. All of the icons are gray and have very little difference except their symbol.
In general, the office MIME icons are nice and bold compared to the text source files which mostly have dull icons.
Can we get bold color in some more icons (like Numix-Circle)?
---
Originally filed by [SuperScript](https://launchpad.net/~superscript18) on [Launchpad](https://bugs.launchpad.net/elementaryicons/+bug/1408834). | 1.0 | Differentiate between code mimes by color - In a folder full of HTML, PHP, JS and CSS files, it is difficult to differentiate between them quickly by color. All of the icons are gray and have very little difference except their symbol.
In general, the office MIME icons are nice and bold compared to the text source files which mostly have dull icons.
Can we get bold color in some more icons (like Numix-Circle)?
---
Originally filed by [SuperScript](https://launchpad.net/~superscript18) on [Launchpad](https://bugs.launchpad.net/elementaryicons/+bug/1408834). | non_design | differentiate between code mimes by color in a folder full of html php js and css files it is difficult to differentiate between them quickly by color all of the icons are gray and have very little difference except their symbol in general the office mime icons are nice and bold compared to the text source files which mostly have dull icons can we get bold color in some more icons like numix circle originally filed by on | 0 |
62,248 | 7,565,334,612 | IssuesEvent | 2018-04-21 08:38:15 | iropensource/groupbot | https://api.github.com/repos/iropensource/groupbot | opened | Database design | Analysis & Design | Read the functionalities expected for the bot which is listed in the issues and create a database model that is suited for this project! in each phase of developing this data model send the database model inside the group!
Google Drive has a collaborative service call draw.io. You can install this tool inside your google drive and work together and discuss about the design together to come up with better design!
You can export the draw.io xml file if you want and send it inside the group till we also check and give you our feedbacks! | 1.0 | Database design - Read the functionalities expected for the bot which is listed in the issues and create a database model that is suited for this project! in each phase of developing this data model send the database model inside the group!
Google Drive has a collaborative service call draw.io. You can install this tool inside your google drive and work together and discuss about the design together to come up with better design!
You can export the draw.io xml file if you want and send it inside the group till we also check and give you our feedbacks! | design | database design read the functionalities expected for the bot which is listed in the issues and create a database model that is suited for this project in each phase of developing this data model send the database model inside the group google drive has a collaborative service call draw io you can install this tool inside your google drive and work together and discuss about the design together to come up with better design you can export the draw io xml file if you want and send it inside the group till we also check and give you our feedbacks | 1 |
52,824 | 10,933,590,432 | IssuesEvent | 2019-11-24 03:36:04 | Binaryify/OneDark-Pro | https://api.github.com/repos/Binaryify/OneDark-Pro | closed | 主题更换出错 | duplicate vscode issue | Issue Type: <b>Feature Request</b>
更换主题颜色时报错:Cannot read property 'id' of undefined
Extension version: 3.0.3
VS Code version: Code 1.40.1 (8795a9889db74563ddd43eb0a897a2384129a619, 2019-11-13T16:49:35.976Z)
OS version: Windows_NT x64 10.0.17763
<!-- generated by issue reporter --> | 1.0 | 主题更换出错 - Issue Type: <b>Feature Request</b>
更换主题颜色时报错:Cannot read property 'id' of undefined
Extension version: 3.0.3
VS Code version: Code 1.40.1 (8795a9889db74563ddd43eb0a897a2384129a619, 2019-11-13T16:49:35.976Z)
OS version: Windows_NT x64 10.0.17763
<!-- generated by issue reporter --> | non_design | 主题更换出错 issue type feature request 更换主题颜色时报错:cannot read property id of undefined extension version vs code version code os version windows nt | 0 |
132,936 | 18,784,956,552 | IssuesEvent | 2021-11-08 11:07:14 | hoprnet/hoprnet-org | https://api.github.com/repos/hoprnet/hoprnet-org | closed | Strange line-spacing | workflow:new issue type:design | # Page
https://hoprnet.org/about-us in the /governance-segment
# Current behavior
# Expected behavior
as above:
| 1.0 | Strange line-spacing - # Page
https://hoprnet.org/about-us in the /governance-segment
# Current behavior
# Expected behavior
as above:
| design | strange line spacing page in the governance segment current behavior expected behavior as above | 1 |
65,934 | 7,933,855,135 | IssuesEvent | 2018-07-08 12:18:17 | unee-t/frontend | https://api.github.com/repos/unee-t/frontend | opened | Update the Signup Page to the new design | design/ux enhancement | # The problem:
In order to be able to do Issue #343 we need to modify the Signup page to:
- Simplify it
- Include the links to the Terms and Conditions and Privacy Policy
- Record the fact that the user has accepted our T&Cs and Privacy Policy in Mongo (see #359)
The link to Unee-T Privacy Policy and Terms and Condition: https://unee-t.com/privacy-and-terms/
# Current design:
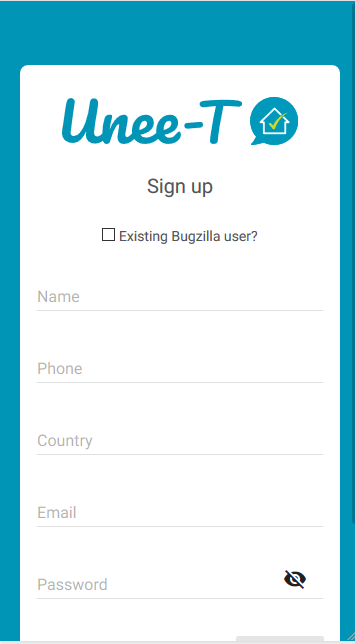
# The design we want:
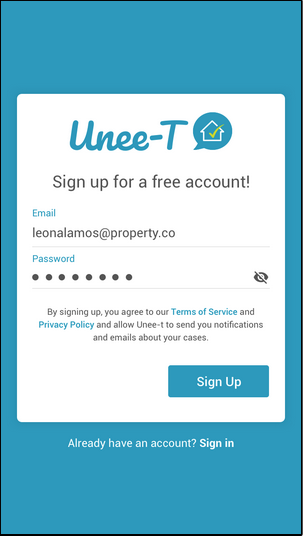
# After the user has Created his/her account:
We need to send the user to the page where he/she can create his/her first unit.
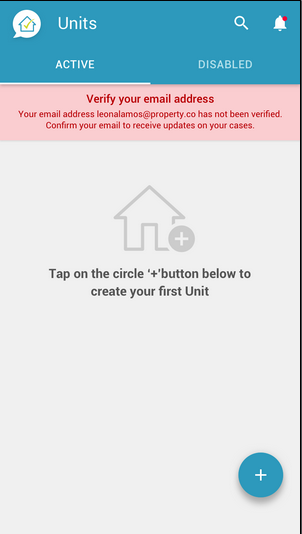
It is OK to ignore the 'verify your email notification message at first. This can be implemented at a later stage.
| 1.0 | Update the Signup Page to the new design - # The problem:
In order to be able to do Issue #343 we need to modify the Signup page to:
- Simplify it
- Include the links to the Terms and Conditions and Privacy Policy
- Record the fact that the user has accepted our T&Cs and Privacy Policy in Mongo (see #359)
The link to Unee-T Privacy Policy and Terms and Condition: https://unee-t.com/privacy-and-terms/
# Current design:
# The design we want:
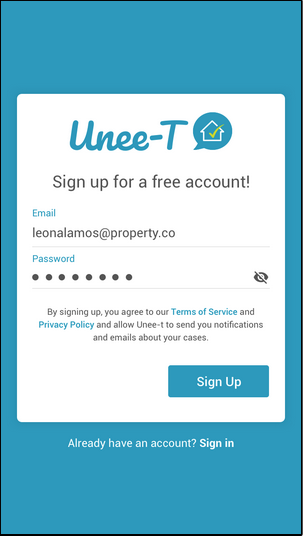
# After the user has Created his/her account:
We need to send the user to the page where he/she can create his/her first unit.
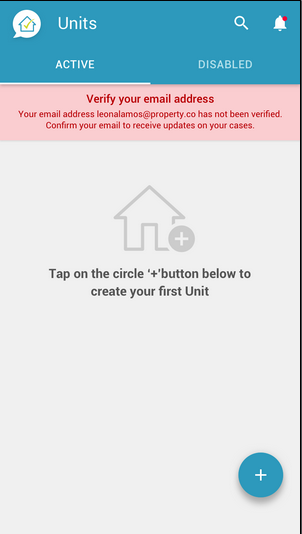
It is OK to ignore the 'verify your email notification message at first. This can be implemented at a later stage.
| design | update the signup page to the new design the problem in order to be able to do issue we need to modify the signup page to simplify it include the links to the terms and conditions and privacy policy record the fact that the user has accepted our t cs and privacy policy in mongo see the link to unee t privacy policy and terms and condition current design the design we want after the user has created his her account we need to send the user to the page where he she can create his her first unit it is ok to ignore the verify your email notification message at first this can be implemented at a later stage | 1 |
22,305 | 2,648,683,821 | IssuesEvent | 2015-03-14 04:38:15 | jeffbryner/MozDef | https://api.github.com/repos/jeffbryner/MozDef | closed | WebUI: Incident Veris Stat visualization enhancement | category:enhancement priority:high | Make use of the pivot table library to allow greater filtering/sorting/playing with veris tags for incidents. | 1.0 | WebUI: Incident Veris Stat visualization enhancement - Make use of the pivot table library to allow greater filtering/sorting/playing with veris tags for incidents. | non_design | webui incident veris stat visualization enhancement make use of the pivot table library to allow greater filtering sorting playing with veris tags for incidents | 0 |
177,393 | 28,490,645,585 | IssuesEvent | 2023-04-18 10:59:08 | baloise-incubator/design-system | https://api.github.com/repos/baloise-incubator/design-system | closed | Add clear function for form controls | 🆕 Enhancement 🎨 Design Support 🧑💻 Technical Design System | As user, I want to be able to delete my input in the search field with one click, so that I save time on deleting every single character. See example attached to this ticket.
Acceptance criteria:
- [ ] Find a way to place a button/icon in input fields in order that the user can delete inputs in a bulk
- [ ] Implement solution

| 2.0 | Add clear function for form controls - As user, I want to be able to delete my input in the search field with one click, so that I save time on deleting every single character. See example attached to this ticket.
Acceptance criteria:
- [ ] Find a way to place a button/icon in input fields in order that the user can delete inputs in a bulk
- [ ] Implement solution

| design | add clear function for form controls as user i want to be able to delete my input in the search field with one click so that i save time on deleting every single character see example attached to this ticket acceptance criteria find a way to place a button icon in input fields in order that the user can delete inputs in a bulk implement solution | 1 |
76,710 | 3,491,153,516 | IssuesEvent | 2016-01-04 14:25:42 | ngageoint/hootenanny-ui | https://api.github.com/repos/ngageoint/hootenanny-ui | opened | Source field is overwritten | Category: UI Priority: High Status: New/Undefined Type: Task | On an attribution copy or conflation, the source field is overwritten, not appended to current. | 1.0 | Source field is overwritten - On an attribution copy or conflation, the source field is overwritten, not appended to current. | non_design | source field is overwritten on an attribution copy or conflation the source field is overwritten not appended to current | 0 |
138,815 | 20,726,831,506 | IssuesEvent | 2022-03-14 03:39:43 | towhee-io/towhee | https://api.github.com/repos/towhee-io/towhee | closed | [DesignProposal]: Auto-Batching in towhee pipeline inference. | design/proposal | ### Background and Motivation
Modern machine learning framework(e.g. PyTorch, Tensorflow) could utilize batch inferencing to improve the throughout. While towhee only support inference the data sequentially, leads to a lower GPU occupancy, we need to add batch inferencing to increase the throughout when we need inference a bunch of data.
### Design
Generally batch mode would consider in two situations.
#### 1 inference a list of data
```python
ppl = pipeline('image-embedding')
outs = ppl(['1.jpg','2.jpg','3.jpg'])
```
#### 2 inference several data in a period
```python
results = []
def callback(output):
lock()
results.append(output)
ppl = pipeline('image-embedding')
with ppl.batch_inference(max_latency=100, max_batch_size=4,callback):
for i in range(10000):
ppl('{}.jpg'.format(i))
```
### Pros and Cons
_No response_
### Anything else? (Additional Context)
_No response_ | 1.0 | [DesignProposal]: Auto-Batching in towhee pipeline inference. - ### Background and Motivation
Modern machine learning framework(e.g. PyTorch, Tensorflow) could utilize batch inferencing to improve the throughout. While towhee only support inference the data sequentially, leads to a lower GPU occupancy, we need to add batch inferencing to increase the throughout when we need inference a bunch of data.
### Design
Generally batch mode would consider in two situations.
#### 1 inference a list of data
```python
ppl = pipeline('image-embedding')
outs = ppl(['1.jpg','2.jpg','3.jpg'])
```
#### 2 inference several data in a period
```python
results = []
def callback(output):
lock()
results.append(output)
ppl = pipeline('image-embedding')
with ppl.batch_inference(max_latency=100, max_batch_size=4,callback):
for i in range(10000):
ppl('{}.jpg'.format(i))
```
### Pros and Cons
_No response_
### Anything else? (Additional Context)
_No response_ | design | auto batching in towhee pipeline inference background and motivation modern machine learning framework e g pytorch tensorflow could utilize batch inferencing to improve the throughout while towhee only support inference the data sequentially leads to a lower gpu occupancy we need to add batch inferencing to increase the throughout when we need inference a bunch of data design generally batch mode would consider in two situations inference a list of data python ppl pipeline image embedding outs ppl inference several data in a period python results def callback output lock results append output ppl pipeline image embedding with ppl batch inference max latency max batch size callback for i in range ppl jpg format i pros and cons no response anything else additional context no response | 1 |
103,958 | 8,955,086,126 | IssuesEvent | 2019-01-26 03:19:21 | numpy/numpy | https://api.github.com/repos/numpy/numpy | opened | azure-pipelines broken for 32-bit compiles. | 05 - Testing | See https://dev.azure.com/numpy/numpy/_build/results?buildId=1943
<!-- Please describe the issue in detail here, and fill in the fields below -->
### Reproducing code example:
<!-- A short code example that reproduces the problem/missing feature. It should be
self-contained, i.e., possible to run as-is via 'python myproblem.py' -->
```python
import numpy as np
<< your code here >>
```
<!-- Remove these sections for a feature request -->
### Error message:
<!-- If you are reporting a segfault please include a GDB traceback, which you
can generate by following
https://github.com/numpy/numpy/blob/master/doc/source/dev/development_environment.rst#debugging -->
<!-- Full error message, if any (starting from line Traceback: ...) -->
### Numpy/Python version information:
<!-- Output from 'import sys, numpy; print(numpy.__version__, sys.version)' -->
| 1.0 | azure-pipelines broken for 32-bit compiles. - See https://dev.azure.com/numpy/numpy/_build/results?buildId=1943
<!-- Please describe the issue in detail here, and fill in the fields below -->
### Reproducing code example:
<!-- A short code example that reproduces the problem/missing feature. It should be
self-contained, i.e., possible to run as-is via 'python myproblem.py' -->
```python
import numpy as np
<< your code here >>
```
<!-- Remove these sections for a feature request -->
### Error message:
<!-- If you are reporting a segfault please include a GDB traceback, which you
can generate by following
https://github.com/numpy/numpy/blob/master/doc/source/dev/development_environment.rst#debugging -->
<!-- Full error message, if any (starting from line Traceback: ...) -->
### Numpy/Python version information:
<!-- Output from 'import sys, numpy; print(numpy.__version__, sys.version)' -->
| non_design | azure pipelines broken for bit compiles see reproducing code example a short code example that reproduces the problem missing feature it should be self contained i e possible to run as is via python myproblem py python import numpy as np error message if you are reporting a segfault please include a gdb traceback which you can generate by following numpy python version information | 0 |
347,798 | 31,276,083,541 | IssuesEvent | 2023-08-22 06:23:13 | farhanramzy/upptime | https://api.github.com/repos/farhanramzy/upptime | opened | 🛑 Test Broken Site22222222 is down | status test-broken-site22222222 | In [`4c4f925`](https://github.com/farhanramzy/upptime/commit/4c4f925bf566f5e111eee664ace2ae77b878661c
), Test Broken Site22222222 (https://thissitedoesnotexist.koj.co) was **down**:
- HTTP code: 0
- Response time: 0 ms
| 1.0 | 🛑 Test Broken Site22222222 is down - In [`4c4f925`](https://github.com/farhanramzy/upptime/commit/4c4f925bf566f5e111eee664ace2ae77b878661c
), Test Broken Site22222222 (https://thissitedoesnotexist.koj.co) was **down**:
- HTTP code: 0
- Response time: 0 ms
| non_design | 🛑 test broken is down in test broken was down http code response time ms | 0 |
362,444 | 25,376,331,283 | IssuesEvent | 2022-11-21 14:22:27 | A-Ozmehak/workmethodology---group-3 | https://api.github.com/repos/A-Ozmehak/workmethodology---group-3 | closed | Set up project with tech stack | documentation Prototype | Needed for this project:
- Set up branch and repo protection rules
- Install: NextJS, Chakra UI, Typescript and Firebase | 1.0 | Set up project with tech stack - Needed for this project:
- Set up branch and repo protection rules
- Install: NextJS, Chakra UI, Typescript and Firebase | non_design | set up project with tech stack needed for this project set up branch and repo protection rules install nextjs chakra ui typescript and firebase | 0 |
165,889 | 6,287,761,804 | IssuesEvent | 2017-07-19 15:33:55 | edcarroll/ng2-semantic-ui | https://api.github.com/repos/edcarroll/ng2-semantic-ui | closed | bug(popup): view destroyed error on popups | comp: popup priority: important type: bug | There are a few cases I'm getting the below error when navigating away from a page containing a popup. A simple replication for Chrome is in this plunkr
http://plnkr.co/edit/4IrG2eK8igIubS2bXN4u
Keep clicking the green button quickly, at some point the popup message will flash out then back in, and the cursor will duplicate so there are two cursors side by side by a few pixels. Navigating away by clicking the page2 link will now give the following error
```
App.html:4 ERROR Error: ViewDestroyedError: Attempt to use a destroyed view: detectChanges
at viewDestroyedError (VM884 core.umd.js:8475)
at Object.debugUpdateDirectives [as updateDirectives] (VM884 core.umd.js:13085)
at checkAndUpdateView (VM884 core.umd.js:12268)
at callWithDebugContext (VM884 core.umd.js:13488)
at Object.debugCheckAndUpdateView [as checkAndUpdateView] (VM884 core.umd.js:13028)
at ViewRef_.detectChanges (VM884 core.umd.js:10199)
at eval (VM884 core.umd.js:4837)
at Array.forEach (<anonymous>)
at ApplicationRef_.tick (VM884 core.umd.js:4837)
at eval (VM884 core.umd.js:4715)
``` | 1.0 | bug(popup): view destroyed error on popups - There are a few cases I'm getting the below error when navigating away from a page containing a popup. A simple replication for Chrome is in this plunkr
http://plnkr.co/edit/4IrG2eK8igIubS2bXN4u
Keep clicking the green button quickly, at some point the popup message will flash out then back in, and the cursor will duplicate so there are two cursors side by side by a few pixels. Navigating away by clicking the page2 link will now give the following error
```
App.html:4 ERROR Error: ViewDestroyedError: Attempt to use a destroyed view: detectChanges
at viewDestroyedError (VM884 core.umd.js:8475)
at Object.debugUpdateDirectives [as updateDirectives] (VM884 core.umd.js:13085)
at checkAndUpdateView (VM884 core.umd.js:12268)
at callWithDebugContext (VM884 core.umd.js:13488)
at Object.debugCheckAndUpdateView [as checkAndUpdateView] (VM884 core.umd.js:13028)
at ViewRef_.detectChanges (VM884 core.umd.js:10199)
at eval (VM884 core.umd.js:4837)
at Array.forEach (<anonymous>)
at ApplicationRef_.tick (VM884 core.umd.js:4837)
at eval (VM884 core.umd.js:4715)
``` | non_design | bug popup view destroyed error on popups there are a few cases i m getting the below error when navigating away from a page containing a popup a simple replication for chrome is in this plunkr keep clicking the green button quickly at some point the popup message will flash out then back in and the cursor will duplicate so there are two cursors side by side by a few pixels navigating away by clicking the link will now give the following error app html error error viewdestroyederror attempt to use a destroyed view detectchanges at viewdestroyederror core umd js at object debugupdatedirectives core umd js at checkandupdateview core umd js at callwithdebugcontext core umd js at object debugcheckandupdateview core umd js at viewref detectchanges core umd js at eval core umd js at array foreach at applicationref tick core umd js at eval core umd js | 0 |
371,924 | 25,973,172,693 | IssuesEvent | 2022-12-19 12:57:36 | alanluqman/RecipeApp | https://api.github.com/repos/alanluqman/RecipeApp | opened | Setup Kanban board | documentation | ### Project :
> RecipeApp
### Team Member :
> 2 people (@alanluqman , @gordonOtieno)
## Project Description
In this Project, my partner and I are working to build a Recipe App | 1.0 | Setup Kanban board - ### Project :
> RecipeApp
### Team Member :
> 2 people (@alanluqman , @gordonOtieno)
## Project Description
In this Project, my partner and I are working to build a Recipe App | non_design | setup kanban board project recipeapp team member people alanluqman gordonotieno project description in this project my partner and i are working to build a recipe app | 0 |
174,138 | 6,537,032,045 | IssuesEvent | 2017-08-31 20:35:43 | redox-os/ion | https://api.github.com/repos/redox-os/ion | closed | src/parser/shell_expand/mod.rs:277 is reachable | bug high-priority | **Reproduction**: [describe how you are able to reproduce ("trigger") this bug/issue.]
```
let PROMPT = "${USER}@${PWD} (${git::branch})"
thread 'main' panicked at 'internal error: entered unreachable code', src/parser/shell_expand/mod.rs:277
note: Run with `RUST_BACKTRACE=1` for a backtrace.
```
see the `@${PWD}` which should have been `\@${PWD}`, but I forgot to backslash it.
**Expected behavior**: [describe the behavior you would expect the repro to yield.]
no crash
**Actual behavior**: [describe the actual behavior, which is presented through the repro.].
**Build information**: [output of `rustc -V`, `git rev-parse HEAD`, `qemu-i386 -version`, `uname -a`, etc.]
$ git rev-parse HEAD
d144f190bdc3fda5760333896fb4511728010326
**Blocking/related**: [issues or PRs blocking or being related to this issue.]
**Misc**: [optional: for other relevant information that should be known or cannot be described in the other fields.]
------
_If the above does not fit the nature of the issue feel free to modify it._
| 1.0 | src/parser/shell_expand/mod.rs:277 is reachable - **Reproduction**: [describe how you are able to reproduce ("trigger") this bug/issue.]
```
let PROMPT = "${USER}@${PWD} (${git::branch})"
thread 'main' panicked at 'internal error: entered unreachable code', src/parser/shell_expand/mod.rs:277
note: Run with `RUST_BACKTRACE=1` for a backtrace.
```
see the `@${PWD}` which should have been `\@${PWD}`, but I forgot to backslash it.
**Expected behavior**: [describe the behavior you would expect the repro to yield.]
no crash
**Actual behavior**: [describe the actual behavior, which is presented through the repro.].
**Build information**: [output of `rustc -V`, `git rev-parse HEAD`, `qemu-i386 -version`, `uname -a`, etc.]
$ git rev-parse HEAD
d144f190bdc3fda5760333896fb4511728010326
**Blocking/related**: [issues or PRs blocking or being related to this issue.]
**Misc**: [optional: for other relevant information that should be known or cannot be described in the other fields.]
------
_If the above does not fit the nature of the issue feel free to modify it._
| non_design | src parser shell expand mod rs is reachable reproduction let prompt user pwd git branch thread main panicked at internal error entered unreachable code src parser shell expand mod rs note run with rust backtrace for a backtrace see the pwd which should have been pwd but i forgot to backslash it expected behavior no crash actual behavior build information git rev parse head blocking related misc if the above does not fit the nature of the issue feel free to modify it | 0 |
63,883 | 7,750,785,581 | IssuesEvent | 2018-05-30 15:12:38 | ParabolInc/action | https://api.github.com/repos/ParabolInc/action | closed | Meeting overview, first-time check in question | design enhancement icebox | ## Issue - Enhancement
Some of our questions are a little esoteric for some users. @tayamueller and I observed folks being stymied by "Heard any good advice lately?" Underlying this, the user doesn't understand the purpose of the check-in round, and how that question relates.
We might need a one-time modal that's like "this is your first meeting, here's what's going to happen," then when they hit check-in round using the most generic question ever, "what is on your mind, that might be keeping you from being fully present?"
- **Estimated effort:** 15 points ([see CONTRIBUTING.md](https://github.com/ParabolInc/action/blob/master/CONTRIBUTING.md#points-and-sizes))
| 1.0 | Meeting overview, first-time check in question - ## Issue - Enhancement
Some of our questions are a little esoteric for some users. @tayamueller and I observed folks being stymied by "Heard any good advice lately?" Underlying this, the user doesn't understand the purpose of the check-in round, and how that question relates.
We might need a one-time modal that's like "this is your first meeting, here's what's going to happen," then when they hit check-in round using the most generic question ever, "what is on your mind, that might be keeping you from being fully present?"
- **Estimated effort:** 15 points ([see CONTRIBUTING.md](https://github.com/ParabolInc/action/blob/master/CONTRIBUTING.md#points-and-sizes))
| design | meeting overview first time check in question issue enhancement some of our questions are a little esoteric for some users tayamueller and i observed folks being stymied by heard any good advice lately underlying this the user doesn t understand the purpose of the check in round and how that question relates we might need a one time modal that s like this is your first meeting here s what s going to happen then when they hit check in round using the most generic question ever what is on your mind that might be keeping you from being fully present estimated effort points | 1 |
155,428 | 12,255,301,332 | IssuesEvent | 2020-05-06 09:58:02 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | opened | TransformSurvivesUpgradeIT#testTransformRollingUpgrade failures | :ml/Transform >test-failure | This has failed three times in the last 8 hours: https://build-stats.elastic.co/app/kibana#/discover?_g=(refreshInterval:(pause:!t,value:0),time:(from:now-12h,mode:quick,to:now))&_a=(columns:!(summary,branch,build-id,stacktrace),index:e58bf320-7efd-11e8-bf69-63c8ef516157,interval:auto,query:(language:lucene,query:testTransformRollingUpgrade),sort:!(time,desc))
The error is
```
org.elasticsearch.upgrades.TransformSurvivesUpgradeIT > testTransformRollingUpgrade FAILED
java.lang.AssertionError:
Expected: a value greater than <2L>
but: <0L> was less than <2L>
at __randomizedtesting.SeedInfo.seed([812C8143CCB7B352:2E51B4FA67F16096]:0)
at org.hamcrest.MatcherAssert.assertThat(MatcherAssert.java:18)
at org.junit.Assert.assertThat(Assert.java:956)
at org.junit.Assert.assertThat(Assert.java:923)
at org.elasticsearch.upgrades.TransformSurvivesUpgradeIT.lambda$waitUntilAfterCheckpoint$11(TransformSurvivesUpgradeIT.java:342)
at org.elasticsearch.test.ESTestCase.assertBusy(ESTestCase.java:892)
at org.elasticsearch.upgrades.TransformSurvivesUpgradeIT.waitUntilAfterCheckpoint(TransformSurvivesUpgradeIT.java:342)
at org.elasticsearch.upgrades.TransformSurvivesUpgradeIT.verifyContinuousTransformHandlesData(TransformSurvivesUpgradeIT.java:231)
at org.elasticsearch.upgrades.TransformSurvivesUpgradeIT.testTransformRollingUpgrade(TransformSurvivesUpgradeIT.java:150)
```
```
REPRODUCE WITH: ./gradlew ':x-pack:qa:rolling-upgrade:v7.8.0#twoThirdsUpgradedTest' --tests "org.elasticsearch.upgrades.TransformSurvivesUpgradeIT.testTransformRollingUpgrade" -Dtests.seed=812C8143CCB7B352 -Dtests.security.manager=true -Dbuild.snapshot=false -Dtests.jvm.argline="-Dbuild.snapshot=false" -Dtests.locale=lt-LT -Dtests.timezone=America/Rainy_River -Dcompiler.java=14 -Druntime.java=11
```
I will mute it for now | 1.0 | TransformSurvivesUpgradeIT#testTransformRollingUpgrade failures - This has failed three times in the last 8 hours: https://build-stats.elastic.co/app/kibana#/discover?_g=(refreshInterval:(pause:!t,value:0),time:(from:now-12h,mode:quick,to:now))&_a=(columns:!(summary,branch,build-id,stacktrace),index:e58bf320-7efd-11e8-bf69-63c8ef516157,interval:auto,query:(language:lucene,query:testTransformRollingUpgrade),sort:!(time,desc))
The error is
```
org.elasticsearch.upgrades.TransformSurvivesUpgradeIT > testTransformRollingUpgrade FAILED
java.lang.AssertionError:
Expected: a value greater than <2L>
but: <0L> was less than <2L>
at __randomizedtesting.SeedInfo.seed([812C8143CCB7B352:2E51B4FA67F16096]:0)
at org.hamcrest.MatcherAssert.assertThat(MatcherAssert.java:18)
at org.junit.Assert.assertThat(Assert.java:956)
at org.junit.Assert.assertThat(Assert.java:923)
at org.elasticsearch.upgrades.TransformSurvivesUpgradeIT.lambda$waitUntilAfterCheckpoint$11(TransformSurvivesUpgradeIT.java:342)
at org.elasticsearch.test.ESTestCase.assertBusy(ESTestCase.java:892)
at org.elasticsearch.upgrades.TransformSurvivesUpgradeIT.waitUntilAfterCheckpoint(TransformSurvivesUpgradeIT.java:342)
at org.elasticsearch.upgrades.TransformSurvivesUpgradeIT.verifyContinuousTransformHandlesData(TransformSurvivesUpgradeIT.java:231)
at org.elasticsearch.upgrades.TransformSurvivesUpgradeIT.testTransformRollingUpgrade(TransformSurvivesUpgradeIT.java:150)
```
```
REPRODUCE WITH: ./gradlew ':x-pack:qa:rolling-upgrade:v7.8.0#twoThirdsUpgradedTest' --tests "org.elasticsearch.upgrades.TransformSurvivesUpgradeIT.testTransformRollingUpgrade" -Dtests.seed=812C8143CCB7B352 -Dtests.security.manager=true -Dbuild.snapshot=false -Dtests.jvm.argline="-Dbuild.snapshot=false" -Dtests.locale=lt-LT -Dtests.timezone=America/Rainy_River -Dcompiler.java=14 -Druntime.java=11
```
I will mute it for now | non_design | transformsurvivesupgradeit testtransformrollingupgrade failures this has failed three times in the last hours the error is org elasticsearch upgrades transformsurvivesupgradeit testtransformrollingupgrade failed java lang assertionerror expected a value greater than but was less than at randomizedtesting seedinfo seed at org hamcrest matcherassert assertthat matcherassert java at org junit assert assertthat assert java at org junit assert assertthat assert java at org elasticsearch upgrades transformsurvivesupgradeit lambda waituntilaftercheckpoint transformsurvivesupgradeit java at org elasticsearch test estestcase assertbusy estestcase java at org elasticsearch upgrades transformsurvivesupgradeit waituntilaftercheckpoint transformsurvivesupgradeit java at org elasticsearch upgrades transformsurvivesupgradeit verifycontinuoustransformhandlesdata transformsurvivesupgradeit java at org elasticsearch upgrades transformsurvivesupgradeit testtransformrollingupgrade transformsurvivesupgradeit java reproduce with gradlew x pack qa rolling upgrade twothirdsupgradedtest tests org elasticsearch upgrades transformsurvivesupgradeit testtransformrollingupgrade dtests seed dtests security manager true dbuild snapshot false dtests jvm argline dbuild snapshot false dtests locale lt lt dtests timezone america rainy river dcompiler java druntime java i will mute it for now | 0 |
146,870 | 23,135,528,079 | IssuesEvent | 2022-07-28 14:03:00 | w3c/wai-aria-practices | https://api.github.com/repos/w3c/wai-aria-practices | closed | Example Pages: Documentation tables have potential F24 failure | bug Feedback Site Design | Not sure if it's a WCAG failure (F24) but Firefox uses my custom colors settings instead of rendering the text black although I've not overridden default color with mine.

The problem comes from the fact that the color of the text is set with `color: initial;`
```
table.data td, table.data th,
table.index td, table.index th,
table.widget-features td, table.widget-features th {
[…]
color: initial;
}
```
Setting the rule to `color: inherit;` fixes it.
See MDN:
> On [inherited properties](https://developer.mozilla.org/en-US/docs/Web/CSS/inheritance#inherited_properties), the initial value may be unexpected. You should consider using the [inherit](https://developer.mozilla.org/en-US/docs/Web/CSS/inherit), [unset](https://developer.mozilla.org/en-US/docs/Web/CSS/unset), [revert](https://developer.mozilla.org/en-US/docs/Web/CSS/revert), or [revert-layer](https://developer.mozilla.org/en-US/docs/Web/CSS/revert-layer) keywords instead. | 1.0 | Example Pages: Documentation tables have potential F24 failure - Not sure if it's a WCAG failure (F24) but Firefox uses my custom colors settings instead of rendering the text black although I've not overridden default color with mine.

The problem comes from the fact that the color of the text is set with `color: initial;`
```
table.data td, table.data th,
table.index td, table.index th,
table.widget-features td, table.widget-features th {
[…]
color: initial;
}
```
Setting the rule to `color: inherit;` fixes it.
See MDN:
> On [inherited properties](https://developer.mozilla.org/en-US/docs/Web/CSS/inheritance#inherited_properties), the initial value may be unexpected. You should consider using the [inherit](https://developer.mozilla.org/en-US/docs/Web/CSS/inherit), [unset](https://developer.mozilla.org/en-US/docs/Web/CSS/unset), [revert](https://developer.mozilla.org/en-US/docs/Web/CSS/revert), or [revert-layer](https://developer.mozilla.org/en-US/docs/Web/CSS/revert-layer) keywords instead. | design | example pages documentation tables have potential failure not sure if it s a wcag failure but firefox uses my custom colors settings instead of rendering the text black although i ve not overridden default color with mine the problem comes from the fact that the color of the text is set with color initial table data td table data th table index td table index th table widget features td table widget features th color initial setting the rule to color inherit fixes it see mdn on the initial value may be unexpected you should consider using the or keywords instead | 1 |
94,100 | 27,113,438,309 | IssuesEvent | 2023-02-15 16:49:20 | opensafely-core/databuilder | https://api.github.com/repos/opensafely-core/databuilder | closed | Improve efficiency of generative tests by making them series-type-aware | databuilder-1 | - [x] Agree design
- [x] Extend new approach to all node types we currently support
- [ ] Experiment to see how long it now takes to generate all nodes types; can we do this as part of the standard build?
- [ ] If the answer to the last question is no, can we instead reduce the number of examples in the standard build to speed up the tests? | 1.0 | Improve efficiency of generative tests by making them series-type-aware - - [x] Agree design
- [x] Extend new approach to all node types we currently support
- [ ] Experiment to see how long it now takes to generate all nodes types; can we do this as part of the standard build?
- [ ] If the answer to the last question is no, can we instead reduce the number of examples in the standard build to speed up the tests? | non_design | improve efficiency of generative tests by making them series type aware agree design extend new approach to all node types we currently support experiment to see how long it now takes to generate all nodes types can we do this as part of the standard build if the answer to the last question is no can we instead reduce the number of examples in the standard build to speed up the tests | 0 |
139,247 | 20,817,767,691 | IssuesEvent | 2022-03-18 12:20:28 | geneontology/go-ontology | https://api.github.com/repos/geneontology/go-ontology | reopened | Change relation for transporters | design pattern logical definitions relations | Hello,
In yesterday's ontology call, it was decided to use 'has primary input' for transporters, rather than 'transports or maintains localization of'.
@vanaukenk @ukemi We need to discuss the plan to retrofit existing annotations
Thanks, Pascale | 1.0 | Change relation for transporters - Hello,
In yesterday's ontology call, it was decided to use 'has primary input' for transporters, rather than 'transports or maintains localization of'.
@vanaukenk @ukemi We need to discuss the plan to retrofit existing annotations
Thanks, Pascale | design | change relation for transporters hello in yesterday s ontology call it was decided to use has primary input for transporters rather than transports or maintains localization of vanaukenk ukemi we need to discuss the plan to retrofit existing annotations thanks pascale | 1 |
119,971 | 15,683,917,071 | IssuesEvent | 2021-03-25 09:22:59 | flutter/flutter | https://api.github.com/repos/flutter/flutter | closed | Material Palette Icon size discrepancy | a: quality f: material design found in release: 1.24 framework has reproducible steps | Icon size btw `Icons.palette_outlined` and `Icons.palette` is different. Here is a short
**Expected results:** <!-- what did you want to see? -->
Expected is both, the outline and the filled to be of the same size such as lightbulb or favorite icons are.
**Actual results:** <!-- what did you see? -->
filled icon is smaller than the outlined one even though both are set to be the same size: 32
<details><summary>Min repro code</summary>
```dart
import 'package:flutter/material.dart';
void main() {
runApp(AmbeeApp());
}
class AmbeeApp extends StatelessWidget {
@override
Widget build(BuildContext context) {
return MaterialApp(
title: 'Ambee 2.0',
home: TabBarScreen(),
);
}
}
/// This is the stateful widget that the main application instantiates.
class TabBarScreen extends StatefulWidget {
@override
_TabBarScreenState createState() => _TabBarScreenState();
}
/// This is the private State class that goes with MyStatefulWidget.
class _TabBarScreenState extends State<TabBarScreen> {
int _selectedIndex = 0;
static const TextStyle optionStyle = TextStyle(fontSize: 30, fontWeight: FontWeight.bold);
static const List<Widget> _widgetOptions = <Widget>[
Text(
'Index 0: Discover',
style: optionStyle,
),
Text(
'Index 1: Favorites',
style: optionStyle,
),
Text(
'Index 2: Lights',
style: optionStyle,
),
];
void _onItemTapped(int index) {
setState(() {
_selectedIndex = index;
});
}
@override
Widget build(BuildContext context) {
return Scaffold(
body: Center(
child: _widgetOptions.elementAt(_selectedIndex),
),
bottomNavigationBar: BottomNavigationBar(
items: const <BottomNavigationBarItem>[
BottomNavigationBarItem(
icon: Icon(Icons.palette_outlined),
activeIcon: Icon(Icons.palette),
label: 'Discover',
),
BottomNavigationBarItem(
icon: Icon(Icons.favorite_outline),
activeIcon: Icon(Icons.favorite),
label: 'Favorites',
),
BottomNavigationBarItem(
icon: Icon(Icons.lightbulb_outline),
activeIcon: Icon(Icons.lightbulb),
label: 'Lights',
),
],
currentIndex: _selectedIndex,
selectedItemColor: Colors.amber[800],
iconSize: 32,
selectedFontSize: 12,
unselectedFontSize: 12,
onTap: _onItemTapped,
),
);
}
}
```
</details>
<details>
<summary>Logs</summary>
<!--
Run your application with `flutter run --verbose` and attach all the
log output below between the lines with the backticks. If there is an
exception, please see if the error message includes enough information
to explain how to solve the issue.
-->
```
```
<!--
Run `flutter analyze` and attach any output of that command below.
If there are any analysis errors, try resolving them before filing this issue.
-->
```
```
<!-- Finally, paste the output of running `flutter doctor -v` here. -->
```
[✓] Flutter (Channel master, 1.24.0-8.0.pre.251, on macOS 11.0.1 20B29 darwin-x64, locale es-ES)
• Flutter version 1.24.0-8.0.pre.251 at /Users/tomas/code/flutter
• Framework revision 836efaecf0 (3 days ago), 2020-11-13 21:51:04 -0800
• Engine revision e06f106385
• Dart version 2.12.0 (build 2.12.0-40.0.dev)
[✗] Android toolchain - develop for Android devices
✗ Unable to locate Android SDK.
Install Android Studio from: https://developer.android.com/studio/index.html
On first launch it will assist you in installing the Android SDK components.
(or visit https://flutter.dev/docs/get-started/install/macos#android-setup for detailed instructions).
If the Android SDK has been installed to a custom location, please use
`flutter config --android-sdk` to update to that location.
[!] Xcode - develop for iOS and macOS (Xcode 12.2)
• Xcode at /Applications/Xcode.app/Contents/Developer
• Xcode 12.2, Build version 12B45b
✗ CocoaPods not installed.
CocoaPods is used to retrieve the iOS and macOS platform side's plugin code that responds to your plugin usage on the Dart side.
Without CocoaPods, plugins will not work on iOS or macOS.
For more info, see https://flutter.dev/platform-plugins
To install see https://guides.cocoapods.org/using/getting-started.html#installation for instructions.
[!] Android Studio (not installed)
• Android Studio not found; download from https://developer.android.com/studio/index.html
(or visit https://flutter.dev/docs/get-started/install/macos#android-setup for detailed instructions).
[✓] VS Code (version 1.51.1)
• VS Code at /Applications/Visual Studio Code.app/Contents
• Flutter extension version 3.16.0
[✓] Connected device (2 available)
• iPhone (mobile) • 00008020-000415840E50003A • ios • iOS 14.2
• iPhone 12 Pro Max (mobile) • CF12B78D-3231-44DD-B217-A38E4A68588B • ios • com.apple.CoreSimulator.SimRuntime.iOS-14-2 (simulator)
! Doctor found issues in 3 categories.
```
</details>
| 1.0 | Material Palette Icon size discrepancy - Icon size btw `Icons.palette_outlined` and `Icons.palette` is different. Here is a short
**Expected results:** <!-- what did you want to see? -->
Expected is both, the outline and the filled to be of the same size such as lightbulb or favorite icons are.
**Actual results:** <!-- what did you see? -->
filled icon is smaller than the outlined one even though both are set to be the same size: 32
<details><summary>Min repro code</summary>
```dart
import 'package:flutter/material.dart';
void main() {
runApp(AmbeeApp());
}
class AmbeeApp extends StatelessWidget {
@override
Widget build(BuildContext context) {
return MaterialApp(
title: 'Ambee 2.0',
home: TabBarScreen(),
);
}
}
/// This is the stateful widget that the main application instantiates.
class TabBarScreen extends StatefulWidget {
@override
_TabBarScreenState createState() => _TabBarScreenState();
}
/// This is the private State class that goes with MyStatefulWidget.
class _TabBarScreenState extends State<TabBarScreen> {
int _selectedIndex = 0;
static const TextStyle optionStyle = TextStyle(fontSize: 30, fontWeight: FontWeight.bold);
static const List<Widget> _widgetOptions = <Widget>[
Text(
'Index 0: Discover',
style: optionStyle,
),
Text(
'Index 1: Favorites',
style: optionStyle,
),
Text(
'Index 2: Lights',
style: optionStyle,
),
];
void _onItemTapped(int index) {
setState(() {
_selectedIndex = index;
});
}
@override
Widget build(BuildContext context) {
return Scaffold(
body: Center(
child: _widgetOptions.elementAt(_selectedIndex),
),
bottomNavigationBar: BottomNavigationBar(
items: const <BottomNavigationBarItem>[
BottomNavigationBarItem(
icon: Icon(Icons.palette_outlined),
activeIcon: Icon(Icons.palette),
label: 'Discover',
),
BottomNavigationBarItem(
icon: Icon(Icons.favorite_outline),
activeIcon: Icon(Icons.favorite),
label: 'Favorites',
),
BottomNavigationBarItem(
icon: Icon(Icons.lightbulb_outline),
activeIcon: Icon(Icons.lightbulb),
label: 'Lights',
),
],
currentIndex: _selectedIndex,
selectedItemColor: Colors.amber[800],
iconSize: 32,
selectedFontSize: 12,
unselectedFontSize: 12,
onTap: _onItemTapped,
),
);
}
}
```
</details>
<details>
<summary>Logs</summary>
<!--
Run your application with `flutter run --verbose` and attach all the
log output below between the lines with the backticks. If there is an
exception, please see if the error message includes enough information
to explain how to solve the issue.
-->
```
```
<!--
Run `flutter analyze` and attach any output of that command below.
If there are any analysis errors, try resolving them before filing this issue.
-->
```
```
<!-- Finally, paste the output of running `flutter doctor -v` here. -->
```
[✓] Flutter (Channel master, 1.24.0-8.0.pre.251, on macOS 11.0.1 20B29 darwin-x64, locale es-ES)
• Flutter version 1.24.0-8.0.pre.251 at /Users/tomas/code/flutter
• Framework revision 836efaecf0 (3 days ago), 2020-11-13 21:51:04 -0800
• Engine revision e06f106385
• Dart version 2.12.0 (build 2.12.0-40.0.dev)
[✗] Android toolchain - develop for Android devices
✗ Unable to locate Android SDK.
Install Android Studio from: https://developer.android.com/studio/index.html
On first launch it will assist you in installing the Android SDK components.
(or visit https://flutter.dev/docs/get-started/install/macos#android-setup for detailed instructions).
If the Android SDK has been installed to a custom location, please use
`flutter config --android-sdk` to update to that location.
[!] Xcode - develop for iOS and macOS (Xcode 12.2)
• Xcode at /Applications/Xcode.app/Contents/Developer
• Xcode 12.2, Build version 12B45b
✗ CocoaPods not installed.
CocoaPods is used to retrieve the iOS and macOS platform side's plugin code that responds to your plugin usage on the Dart side.
Without CocoaPods, plugins will not work on iOS or macOS.
For more info, see https://flutter.dev/platform-plugins
To install see https://guides.cocoapods.org/using/getting-started.html#installation for instructions.
[!] Android Studio (not installed)
• Android Studio not found; download from https://developer.android.com/studio/index.html
(or visit https://flutter.dev/docs/get-started/install/macos#android-setup for detailed instructions).
[✓] VS Code (version 1.51.1)
• VS Code at /Applications/Visual Studio Code.app/Contents
• Flutter extension version 3.16.0
[✓] Connected device (2 available)
• iPhone (mobile) • 00008020-000415840E50003A • ios • iOS 14.2
• iPhone 12 Pro Max (mobile) • CF12B78D-3231-44DD-B217-A38E4A68588B • ios • com.apple.CoreSimulator.SimRuntime.iOS-14-2 (simulator)
! Doctor found issues in 3 categories.
```
</details>
| design | material palette icon size discrepancy icon size btw icons palette outlined and icons palette is different here is a short expected results expected is both the outline and the filled to be of the same size such as lightbulb or favorite icons are actual results filled icon is smaller than the outlined one even though both are set to be the same size min repro code dart import package flutter material dart void main runapp ambeeapp class ambeeapp extends statelesswidget override widget build buildcontext context return materialapp title ambee home tabbarscreen this is the stateful widget that the main application instantiates class tabbarscreen extends statefulwidget override tabbarscreenstate createstate tabbarscreenstate this is the private state class that goes with mystatefulwidget class tabbarscreenstate extends state int selectedindex static const textstyle optionstyle textstyle fontsize fontweight fontweight bold static const list widgetoptions text index discover style optionstyle text index favorites style optionstyle text index lights style optionstyle void onitemtapped int index setstate selectedindex index override widget build buildcontext context return scaffold body center child widgetoptions elementat selectedindex bottomnavigationbar bottomnavigationbar items const bottomnavigationbaritem icon icon icons palette outlined activeicon icon icons palette label discover bottomnavigationbaritem icon icon icons favorite outline activeicon icon icons favorite label favorites bottomnavigationbaritem icon icon icons lightbulb outline activeicon icon icons lightbulb label lights currentindex selectedindex selecteditemcolor colors amber iconsize selectedfontsize unselectedfontsize ontap onitemtapped logs run your application with flutter run verbose and attach all the log output below between the lines with the backticks if there is an exception please see if the error message includes enough information to explain how to solve the issue run flutter analyze and attach any output of that command below if there are any analysis errors try resolving them before filing this issue flutter channel master pre on macos darwin locale es es • flutter version pre at users tomas code flutter • framework revision days ago • engine revision • dart version build dev android toolchain develop for android devices ✗ unable to locate android sdk install android studio from on first launch it will assist you in installing the android sdk components or visit for detailed instructions if the android sdk has been installed to a custom location please use flutter config android sdk to update to that location xcode develop for ios and macos xcode • xcode at applications xcode app contents developer • xcode build version ✗ cocoapods not installed cocoapods is used to retrieve the ios and macos platform side s plugin code that responds to your plugin usage on the dart side without cocoapods plugins will not work on ios or macos for more info see to install see for instructions android studio not installed • android studio not found download from or visit for detailed instructions vs code version • vs code at applications visual studio code app contents • flutter extension version connected device available • iphone mobile • • ios • ios • iphone pro max mobile • • ios • com apple coresimulator simruntime ios simulator doctor found issues in categories | 1 |
27,761 | 4,065,104,392 | IssuesEvent | 2016-05-26 09:49:12 | oSlashStudio/Faux-G | https://api.github.com/repos/oSlashStudio/Faux-G | opened | The laser sight on crosshair cannot be colored red | design question | The crosshair itself is colored green but the laser sight need to be in red. | 1.0 | The laser sight on crosshair cannot be colored red - The crosshair itself is colored green but the laser sight need to be in red. | design | the laser sight on crosshair cannot be colored red the crosshair itself is colored green but the laser sight need to be in red | 1 |
74,777 | 9,115,480,914 | IssuesEvent | 2019-02-22 05:13:02 | aspnet/AspNetCore | https://api.github.com/repos/aspnet/AspNetCore | closed | Inifinite loop during model binding when using [ModelBinder] attribute | 2 - Working PRI: 1 - Required area-mvc enhancement feature-Model-Binding needs design | #### Is this a Bug or Feature request?:
Bug
#### Steps to reproduce (preferably a link to a GitHub repo with a repro project):
Link to repro: https://github.com/Costo/aspnetcore-binding-bug
* Run project with `dotnet run`
* Go to https://localhost:5001
* Submit the Form
Expected result:
* Form is submitted and server responds with 200 OK
Actual result:
* Server never responds. If you attach a debugger and add a breakpoint to `NumberModelBinder.BindModelAsync`, you can see that the program is in an inifinite loop (see screenshot below).

#### Description of the problem:
The problem occurs when using a custom Model Binder for a decimal property in this model:
```cs
public class TestModel
{
public TestInnerModel[] InnerModels { get; set; } = new TestInnerModel[0];
}
public class TestInnerModel
{
public TestInnerModel()
{
}
[ModelBinder(BinderType = typeof(NumberModelBinder))]
public decimal Rate { get; set; }
}
```
During a POST, it seems that model binding is stuck in an infinite loop in [CollectionModelBinder](https://github.com/aspnet/Mvc/blob/5ed7658bf221fe136d8cedafe4c3466ed19726a3/src/Microsoft.AspNetCore.Mvc.Core/ModelBinding/Binders/CollectionModelBinder.cs#L340)
The code of the `NumberModelBinder` class is actually the code of [DecimalModelBinder](https://github.com/aspnet/Mvc/blob/master/src/Microsoft.AspNetCore.Mvc.Core/ModelBinding/Binders/DecimalModelBinder.cs), with internal logging code stripped out, so nothing out of the ordinary.
If the `[ModelBinder]` attribute is removed, the application works fine.
#### Version of `Microsoft.AspNetCore.Mvc` or `Microsoft.AspNetCore.App` or `Microsoft.AspNetCore.All`:
`netcoreapp2.1` or `netcoreapp2.2` with SDK `2.2.100-preview3-009430`
| 1.0 | Inifinite loop during model binding when using [ModelBinder] attribute - #### Is this a Bug or Feature request?:
Bug
#### Steps to reproduce (preferably a link to a GitHub repo with a repro project):
Link to repro: https://github.com/Costo/aspnetcore-binding-bug
* Run project with `dotnet run`
* Go to https://localhost:5001
* Submit the Form
Expected result:
* Form is submitted and server responds with 200 OK
Actual result:
* Server never responds. If you attach a debugger and add a breakpoint to `NumberModelBinder.BindModelAsync`, you can see that the program is in an inifinite loop (see screenshot below).

#### Description of the problem:
The problem occurs when using a custom Model Binder for a decimal property in this model:
```cs
public class TestModel
{
public TestInnerModel[] InnerModels { get; set; } = new TestInnerModel[0];
}
public class TestInnerModel
{
public TestInnerModel()
{
}
[ModelBinder(BinderType = typeof(NumberModelBinder))]
public decimal Rate { get; set; }
}
```
During a POST, it seems that model binding is stuck in an infinite loop in [CollectionModelBinder](https://github.com/aspnet/Mvc/blob/5ed7658bf221fe136d8cedafe4c3466ed19726a3/src/Microsoft.AspNetCore.Mvc.Core/ModelBinding/Binders/CollectionModelBinder.cs#L340)
The code of the `NumberModelBinder` class is actually the code of [DecimalModelBinder](https://github.com/aspnet/Mvc/blob/master/src/Microsoft.AspNetCore.Mvc.Core/ModelBinding/Binders/DecimalModelBinder.cs), with internal logging code stripped out, so nothing out of the ordinary.
If the `[ModelBinder]` attribute is removed, the application works fine.
#### Version of `Microsoft.AspNetCore.Mvc` or `Microsoft.AspNetCore.App` or `Microsoft.AspNetCore.All`:
`netcoreapp2.1` or `netcoreapp2.2` with SDK `2.2.100-preview3-009430`
| design | inifinite loop during model binding when using attribute is this a bug or feature request bug steps to reproduce preferably a link to a github repo with a repro project link to repro run project with dotnet run go to submit the form expected result form is submitted and server responds with ok actual result server never responds if you attach a debugger and add a breakpoint to numbermodelbinder bindmodelasync you can see that the program is in an inifinite loop see screenshot below description of the problem the problem occurs when using a custom model binder for a decimal property in this model cs public class testmodel public testinnermodel innermodels get set new testinnermodel public class testinnermodel public testinnermodel public decimal rate get set during a post it seems that model binding is stuck in an infinite loop in the code of the numbermodelbinder class is actually the code of with internal logging code stripped out so nothing out of the ordinary if the attribute is removed the application works fine version of microsoft aspnetcore mvc or microsoft aspnetcore app or microsoft aspnetcore all or with sdk | 1 |
28,943 | 4,151,569,021 | IssuesEvent | 2016-06-15 21:02:10 | jondaiello/jondaiello-com | https://api.github.com/repos/jondaiello/jondaiello-com | closed | Update Blockquote style | design | ```
.article-content blockquote {
margin-left: -224px;
width: 100vw;
padding-left: 1.5em;
padding-right: 1.5em;
background: #f5f5f5;
padding: .2em 1.5em;
margin-top: .5em;
margin-bottom: .5em;
}
blockquote {
color: #aaa; /* or color: #999; */
}
``` | 1.0 | Update Blockquote style - ```
.article-content blockquote {
margin-left: -224px;
width: 100vw;
padding-left: 1.5em;
padding-right: 1.5em;
background: #f5f5f5;
padding: .2em 1.5em;
margin-top: .5em;
margin-bottom: .5em;
}
blockquote {
color: #aaa; /* or color: #999; */
}
``` | design | update blockquote style article content blockquote margin left width padding left padding right background padding margin top margin bottom blockquote color aaa or color | 1 |
365,565 | 25,542,177,927 | IssuesEvent | 2022-11-29 16:02:41 | celestiaorg/docs | https://api.github.com/repos/celestiaorg/docs | closed | Tutorial on Running an Ethermint-Tendermint Node | documentation | [Running an Astria Node](https://github.com/celestiaorg/ephemeral-cluster/blob/main/docker/ethermint/ethermint-docker-compose.yml)
* Wait on this [PR](https://github.com/celestiaorg/ephemeral-cluster/pull/23)
[Script](https://github.com/celestiaorg/ephemeral-cluster/blob/main/scripts/minimal-ethermint.sh)
* Set the version of Ethermint via a flag
* `export ETHERMINT_IMAGE_TAG=sha-02075c6`
* https://github.com/celestiaorg/ethermint/pkgs/container/ethermint
* https://github.com/celestiaorg/ephemeral-cluster#ephemeral-cluster | 1.0 | Tutorial on Running an Ethermint-Tendermint Node - [Running an Astria Node](https://github.com/celestiaorg/ephemeral-cluster/blob/main/docker/ethermint/ethermint-docker-compose.yml)
* Wait on this [PR](https://github.com/celestiaorg/ephemeral-cluster/pull/23)
[Script](https://github.com/celestiaorg/ephemeral-cluster/blob/main/scripts/minimal-ethermint.sh)
* Set the version of Ethermint via a flag
* `export ETHERMINT_IMAGE_TAG=sha-02075c6`
* https://github.com/celestiaorg/ethermint/pkgs/container/ethermint
* https://github.com/celestiaorg/ephemeral-cluster#ephemeral-cluster | non_design | tutorial on running an ethermint tendermint node wait on this set the version of ethermint via a flag export ethermint image tag sha | 0 |
801,443 | 28,489,201,878 | IssuesEvent | 2023-04-18 10:01:27 | googleapis/java-spanner-jdbc | https://api.github.com/repos/googleapis/java-spanner-jdbc | opened | spanner.jdbc.it.ITJdbcPgDatabaseMetaDataTest: testGetExportedKeys failed | priority: p1 type: bug flakybot: issue | Note: #813 was also for this test, but it was closed more than 10 days ago. So, I didn't mark it flaky.
----
commit: 76fc16a7651120ac019ad13ca2c2e4bccd2bd7a1
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/3a5befd1-d3c8-4987-86b1-a2e6c980b527), [Sponge](http://sponge2/3a5befd1-d3c8-4987-86b1-a2e6c980b527)
status: failed
<details><summary>Test output</summary><br><pre>com.google.cloud.spanner.SpannerException: UNAVAILABLE: com.google.cloud.spanner.SpannerException: UNAVAILABLE: com.google.api.gax.rpc.UnavailableException: io.grpc.StatusRuntimeException: UNAVAILABLE: Credentials failed to obtain metadata
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerExceptionPreformatted(SpannerExceptionFactory.java:291)
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerExceptionPreformatted(SpannerExceptionFactory.java:297)
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerException(SpannerExceptionFactory.java:61)
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerException(SpannerExceptionFactory.java:181)
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerException(SpannerExceptionFactory.java:110)
at com.google.cloud.spanner.SpannerExceptionFactory.asSpannerException(SpannerExceptionFactory.java:100)
at com.google.cloud.spanner.SessionPool.getDialect(SessionPool.java:1992)
at com.google.cloud.spanner.DatabaseClientImpl.getDialect(DatabaseClientImpl.java:59)
at com.google.cloud.spanner.connection.ConnectionImpl.getDialect(ConnectionImpl.java:354)
at com.google.cloud.spanner.jdbc.AbstractJdbcConnection.getDialect(AbstractJdbcConnection.java:85)
at com.google.cloud.spanner.jdbc.JdbcDatabaseMetaData.getExportedKeys(JdbcDatabaseMetaData.java:890)
at com.google.cloud.spanner.jdbc.it.ITJdbcPgDatabaseMetaDataTest.testGetExportedKeys(ITJdbcPgDatabaseMetaDataTest.java:493)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:59)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:56)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at org.junit.internal.runners.statements.RunBefores.evaluate(RunBefores.java:26)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.BlockJUnit4ClassRunner$1.evaluate(BlockJUnit4ClassRunner.java:100)
at org.junit.runners.ParentRunner.runLeaf(ParentRunner.java:366)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:103)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:63)
at org.junit.runners.ParentRunner$4.run(ParentRunner.java:331)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:79)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:329)
at org.junit.runners.ParentRunner.access$100(ParentRunner.java:66)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:293)
at org.junit.internal.runners.statements.RunBefores.evaluate(RunBefores.java:26)
at org.junit.rules.ExternalResource$1.evaluate(ExternalResource.java:54)
at org.junit.rules.RunRules.evaluate(RunRules.java:20)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.ParentRunner.run(ParentRunner.java:413)
at org.junit.runners.Suite.runChild(Suite.java:128)
at org.junit.runners.Suite.runChild(Suite.java:27)
at org.junit.runners.ParentRunner$4.run(ParentRunner.java:331)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:79)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:329)
at org.junit.runners.ParentRunner.access$100(ParentRunner.java:66)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:293)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.ParentRunner.run(ParentRunner.java:413)
at org.apache.maven.surefire.junitcore.JUnitCore.run(JUnitCore.java:55)
at org.apache.maven.surefire.junitcore.JUnitCoreWrapper.createRequestAndRun(JUnitCoreWrapper.java:137)
at org.apache.maven.surefire.junitcore.JUnitCoreWrapper.executeLazy(JUnitCoreWrapper.java:119)
at org.apache.maven.surefire.junitcore.JUnitCoreWrapper.execute(JUnitCoreWrapper.java:87)
at org.apache.maven.surefire.junitcore.JUnitCoreWrapper.execute(JUnitCoreWrapper.java:75)
at org.apache.maven.surefire.junitcore.JUnitCoreProvider.invoke(JUnitCoreProvider.java:158)
at org.apache.maven.surefire.booter.ForkedBooter.runSuitesInProcess(ForkedBooter.java:456)
at org.apache.maven.surefire.booter.ForkedBooter.execute(ForkedBooter.java:169)
at org.apache.maven.surefire.booter.ForkedBooter.run(ForkedBooter.java:595)
at org.apache.maven.surefire.booter.ForkedBooter.main(ForkedBooter.java:581)
Caused by: java.util.concurrent.ExecutionException: com.google.cloud.spanner.SpannerException: UNAVAILABLE: com.google.api.gax.rpc.UnavailableException: io.grpc.StatusRuntimeException: UNAVAILABLE: Credentials failed to obtain metadata
at com.google.common.util.concurrent.AbstractFuture.getDoneValue(AbstractFuture.java:588)
at com.google.common.util.concurrent.AbstractFuture.get(AbstractFuture.java:439)
at com.google.common.util.concurrent.AbstractFuture$TrustedFuture.get(AbstractFuture.java:121)
at com.google.cloud.spanner.SessionPool.getDialect(SessionPool.java:1990)
... 48 more
Caused by: com.google.cloud.spanner.SpannerException: UNAVAILABLE: com.google.api.gax.rpc.UnavailableException: io.grpc.StatusRuntimeException: UNAVAILABLE: Credentials failed to obtain metadata
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerExceptionPreformatted(SpannerExceptionFactory.java:291)
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerExceptionPreformatted(SpannerExceptionFactory.java:297)
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerException(SpannerExceptionFactory.java:170)
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerException(SpannerExceptionFactory.java:110)
at com.google.cloud.spanner.SessionPool$SessionConsumerImpl.onSessionCreateFailure(SessionPool.java:2470)
at com.google.cloud.spanner.SessionClient$BatchCreateSessionsRunnable.run(SessionClient.java:140)
at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
at java.util.concurrent.FutureTask.run(FutureTask.java:266)
at java.util.concurrent.ScheduledThreadPoolExecutor$ScheduledFutureTask.access$201(ScheduledThreadPoolExecutor.java:180)
at java.util.concurrent.ScheduledThreadPoolExecutor$ScheduledFutureTask.run(ScheduledThreadPoolExecutor.java:293)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
at java.lang.Thread.run(Thread.java:750)
Caused by: com.google.cloud.spanner.SpannerException: UNAVAILABLE: com.google.api.gax.rpc.UnavailableException: io.grpc.StatusRuntimeException: UNAVAILABLE: Credentials failed to obtain metadata
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerExceptionPreformatted(SpannerExceptionFactory.java:291)
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerExceptionPreformatted(SpannerExceptionFactory.java:297)
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerException(SpannerExceptionFactory.java:61)
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerException(SpannerExceptionFactory.java:181)
at com.google.cloud.spanner.spi.v1.GapicSpannerRpc.get(GapicSpannerRpc.java:1883)
at com.google.cloud.spanner.spi.v1.GapicSpannerRpc.batchCreateSessions(GapicSpannerRpc.java:1596)
at com.google.cloud.spanner.SessionClient.internalBatchCreateSessions(SessionClient.java:303)
at com.google.cloud.spanner.SessionClient.access$000(SessionClient.java:38)
at com.google.cloud.spanner.SessionClient$BatchCreateSessionsRunnable.run(SessionClient.java:137)
... 7 more
Caused by: java.util.concurrent.ExecutionException: com.google.api.gax.rpc.UnavailableException: io.grpc.StatusRuntimeException: UNAVAILABLE: Credentials failed to obtain metadata
at com.google.common.util.concurrent.AbstractFuture.getDoneValue(AbstractFuture.java:588)
at com.google.common.util.concurrent.AbstractFuture.get(AbstractFuture.java:567)
at com.google.cloud.spanner.spi.v1.GapicSpannerRpc.get(GapicSpannerRpc.java:1877)
... 11 more
Caused by: com.google.api.gax.rpc.UnavailableException: io.grpc.StatusRuntimeException: UNAVAILABLE: Credentials failed to obtain metadata
at com.google.api.gax.rpc.ApiExceptionFactory.createException(ApiExceptionFactory.java:112)
at com.google.api.gax.rpc.ApiExceptionFactory.createException(ApiExceptionFactory.java:41)
at com.google.api.gax.grpc.GrpcApiExceptionFactory.create(GrpcApiExceptionFactory.java:86)
at com.google.api.gax.grpc.GrpcApiExceptionFactory.create(GrpcApiExceptionFactory.java:66)
at com.google.api.gax.grpc.GrpcExceptionCallable$ExceptionTransformingFuture.onFailure(GrpcExceptionCallable.java:97)
at com.google.api.core.ApiFutures$1.onFailure(ApiFutures.java:67)
at com.google.common.util.concurrent.Futures$CallbackListener.run(Futures.java:1132)
at com.google.common.util.concurrent.DirectExecutor.execute(DirectExecutor.java:31)
at com.google.common.util.concurrent.AbstractFuture.executeListener(AbstractFuture.java:1270)
at com.google.common.util.concurrent.AbstractFuture.complete(AbstractFuture.java:1038)
at com.google.common.util.concurrent.AbstractFuture.setException(AbstractFuture.java:808)
at io.grpc.stub.ClientCalls$GrpcFuture.setException(ClientCalls.java:574)
at io.grpc.stub.ClientCalls$UnaryStreamToFuture.onClose(ClientCalls.java:544)
at io.grpc.PartialForwardingClientCallListener.onClose(PartialForwardingClientCallListener.java:39)
at io.grpc.ForwardingClientCallListener.onClose(ForwardingClientCallListener.java:23)
at io.grpc.ForwardingClientCallListener$SimpleForwardingClientCallListener.onClose(ForwardingClientCallListener.java:40)
at com.google.api.gax.grpc.ChannelPool$ReleasingClientCall$1.onClose(ChannelPool.java:541)
at io.grpc.PartialForwardingClientCallListener.onClose(PartialForwardingClientCallListener.java:39)
at io.grpc.ForwardingClientCallListener.onClose(ForwardingClientCallListener.java:23)
at io.grpc.ForwardingClientCallListener$SimpleForwardingClientCallListener.onClose(ForwardingClientCallListener.java:40)
at io.grpc.PartialForwardingClientCallListener.onClose(PartialForwardingClientCallListener.java:39)
at io.grpc.ForwardingClientCallListener.onClose(ForwardingClientCallListener.java:23)
at io.grpc.ForwardingClientCallListener$SimpleForwardingClientCallListener.onClose(ForwardingClientCallListener.java:40)
at com.google.cloud.spanner.spi.v1.SpannerErrorInterceptor$1$1.onClose(SpannerErrorInterceptor.java:100)
at io.grpc.internal.ClientCallImpl.closeObserver(ClientCallImpl.java:576)
at io.grpc.internal.ClientCallImpl.access$300(ClientCallImpl.java:70)
at io.grpc.internal.ClientCallImpl$ClientStreamListenerImpl$1StreamClosed.runInternal(ClientCallImpl.java:757)
at io.grpc.internal.ClientCallImpl$ClientStreamListenerImpl$1StreamClosed.runInContext(ClientCallImpl.java:736)
at io.grpc.internal.ContextRunnable.run(ContextRunnable.java:37)
at io.grpc.internal.SerializingExecutor.run(SerializingExecutor.java:133)
... 7 more
Caused by: io.grpc.StatusRuntimeException: UNAVAILABLE: Credentials failed to obtain metadata
at io.grpc.Status.asRuntimeException(Status.java:539)
... 25 more
Caused by: com.google.auth.oauth2.GoogleAuthException: Error getting access token for service account: 400 Bad Request
POST https://oauth2.googleapis.com/token
{"error":"invalid_grant","error_description":"Invalid JWT Signature."}, iss: java-client-testing@span-cloud-testing.iam.gserviceaccount.com
at com.google.auth.oauth2.GoogleAuthException.createWithTokenEndpointResponseException(GoogleAuthException.java:131)
at com.google.auth.oauth2.ServiceAccountCredentials.refreshAccessToken(ServiceAccountCredentials.java:541)
at com.google.auth.oauth2.OAuth2Credentials$1.call(OAuth2Credentials.java:269)
at com.google.auth.oauth2.OAuth2Credentials$1.call(OAuth2Credentials.java:266)
at java.util.concurrent.FutureTask.run(FutureTask.java:266)
at com.google.auth.oauth2.OAuth2Credentials$RefreshTask.run(OAuth2Credentials.java:633)
... 3 more
Caused by: com.google.api.client.http.HttpResponseException: 400 Bad Request
POST https://oauth2.googleapis.com/token
{"error":"invalid_grant","error_description":"Invalid JWT Signature."}
at com.google.api.client.http.HttpResponseException$Builder.build(HttpResponseException.java:293)
at com.google.api.client.http.HttpRequest.execute(HttpRequest.java:1118)
at com.google.auth.oauth2.ServiceAccountCredentials.refreshAccessToken(ServiceAccountCredentials.java:538)
... 7 more
</pre></details> | 1.0 | spanner.jdbc.it.ITJdbcPgDatabaseMetaDataTest: testGetExportedKeys failed - Note: #813 was also for this test, but it was closed more than 10 days ago. So, I didn't mark it flaky.
----
commit: 76fc16a7651120ac019ad13ca2c2e4bccd2bd7a1
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/3a5befd1-d3c8-4987-86b1-a2e6c980b527), [Sponge](http://sponge2/3a5befd1-d3c8-4987-86b1-a2e6c980b527)
status: failed
<details><summary>Test output</summary><br><pre>com.google.cloud.spanner.SpannerException: UNAVAILABLE: com.google.cloud.spanner.SpannerException: UNAVAILABLE: com.google.api.gax.rpc.UnavailableException: io.grpc.StatusRuntimeException: UNAVAILABLE: Credentials failed to obtain metadata
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerExceptionPreformatted(SpannerExceptionFactory.java:291)
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerExceptionPreformatted(SpannerExceptionFactory.java:297)
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerException(SpannerExceptionFactory.java:61)
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerException(SpannerExceptionFactory.java:181)
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerException(SpannerExceptionFactory.java:110)
at com.google.cloud.spanner.SpannerExceptionFactory.asSpannerException(SpannerExceptionFactory.java:100)
at com.google.cloud.spanner.SessionPool.getDialect(SessionPool.java:1992)
at com.google.cloud.spanner.DatabaseClientImpl.getDialect(DatabaseClientImpl.java:59)
at com.google.cloud.spanner.connection.ConnectionImpl.getDialect(ConnectionImpl.java:354)
at com.google.cloud.spanner.jdbc.AbstractJdbcConnection.getDialect(AbstractJdbcConnection.java:85)
at com.google.cloud.spanner.jdbc.JdbcDatabaseMetaData.getExportedKeys(JdbcDatabaseMetaData.java:890)
at com.google.cloud.spanner.jdbc.it.ITJdbcPgDatabaseMetaDataTest.testGetExportedKeys(ITJdbcPgDatabaseMetaDataTest.java:493)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:59)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:56)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at org.junit.internal.runners.statements.RunBefores.evaluate(RunBefores.java:26)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.BlockJUnit4ClassRunner$1.evaluate(BlockJUnit4ClassRunner.java:100)
at org.junit.runners.ParentRunner.runLeaf(ParentRunner.java:366)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:103)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:63)
at org.junit.runners.ParentRunner$4.run(ParentRunner.java:331)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:79)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:329)
at org.junit.runners.ParentRunner.access$100(ParentRunner.java:66)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:293)
at org.junit.internal.runners.statements.RunBefores.evaluate(RunBefores.java:26)
at org.junit.rules.ExternalResource$1.evaluate(ExternalResource.java:54)
at org.junit.rules.RunRules.evaluate(RunRules.java:20)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.ParentRunner.run(ParentRunner.java:413)
at org.junit.runners.Suite.runChild(Suite.java:128)
at org.junit.runners.Suite.runChild(Suite.java:27)
at org.junit.runners.ParentRunner$4.run(ParentRunner.java:331)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:79)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:329)
at org.junit.runners.ParentRunner.access$100(ParentRunner.java:66)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:293)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.ParentRunner.run(ParentRunner.java:413)
at org.apache.maven.surefire.junitcore.JUnitCore.run(JUnitCore.java:55)
at org.apache.maven.surefire.junitcore.JUnitCoreWrapper.createRequestAndRun(JUnitCoreWrapper.java:137)
at org.apache.maven.surefire.junitcore.JUnitCoreWrapper.executeLazy(JUnitCoreWrapper.java:119)
at org.apache.maven.surefire.junitcore.JUnitCoreWrapper.execute(JUnitCoreWrapper.java:87)
at org.apache.maven.surefire.junitcore.JUnitCoreWrapper.execute(JUnitCoreWrapper.java:75)
at org.apache.maven.surefire.junitcore.JUnitCoreProvider.invoke(JUnitCoreProvider.java:158)
at org.apache.maven.surefire.booter.ForkedBooter.runSuitesInProcess(ForkedBooter.java:456)
at org.apache.maven.surefire.booter.ForkedBooter.execute(ForkedBooter.java:169)
at org.apache.maven.surefire.booter.ForkedBooter.run(ForkedBooter.java:595)
at org.apache.maven.surefire.booter.ForkedBooter.main(ForkedBooter.java:581)
Caused by: java.util.concurrent.ExecutionException: com.google.cloud.spanner.SpannerException: UNAVAILABLE: com.google.api.gax.rpc.UnavailableException: io.grpc.StatusRuntimeException: UNAVAILABLE: Credentials failed to obtain metadata
at com.google.common.util.concurrent.AbstractFuture.getDoneValue(AbstractFuture.java:588)
at com.google.common.util.concurrent.AbstractFuture.get(AbstractFuture.java:439)
at com.google.common.util.concurrent.AbstractFuture$TrustedFuture.get(AbstractFuture.java:121)
at com.google.cloud.spanner.SessionPool.getDialect(SessionPool.java:1990)
... 48 more
Caused by: com.google.cloud.spanner.SpannerException: UNAVAILABLE: com.google.api.gax.rpc.UnavailableException: io.grpc.StatusRuntimeException: UNAVAILABLE: Credentials failed to obtain metadata
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerExceptionPreformatted(SpannerExceptionFactory.java:291)
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerExceptionPreformatted(SpannerExceptionFactory.java:297)
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerException(SpannerExceptionFactory.java:170)
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerException(SpannerExceptionFactory.java:110)
at com.google.cloud.spanner.SessionPool$SessionConsumerImpl.onSessionCreateFailure(SessionPool.java:2470)
at com.google.cloud.spanner.SessionClient$BatchCreateSessionsRunnable.run(SessionClient.java:140)
at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
at java.util.concurrent.FutureTask.run(FutureTask.java:266)
at java.util.concurrent.ScheduledThreadPoolExecutor$ScheduledFutureTask.access$201(ScheduledThreadPoolExecutor.java:180)
at java.util.concurrent.ScheduledThreadPoolExecutor$ScheduledFutureTask.run(ScheduledThreadPoolExecutor.java:293)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
at java.lang.Thread.run(Thread.java:750)
Caused by: com.google.cloud.spanner.SpannerException: UNAVAILABLE: com.google.api.gax.rpc.UnavailableException: io.grpc.StatusRuntimeException: UNAVAILABLE: Credentials failed to obtain metadata
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerExceptionPreformatted(SpannerExceptionFactory.java:291)
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerExceptionPreformatted(SpannerExceptionFactory.java:297)
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerException(SpannerExceptionFactory.java:61)
at com.google.cloud.spanner.SpannerExceptionFactory.newSpannerException(SpannerExceptionFactory.java:181)
at com.google.cloud.spanner.spi.v1.GapicSpannerRpc.get(GapicSpannerRpc.java:1883)
at com.google.cloud.spanner.spi.v1.GapicSpannerRpc.batchCreateSessions(GapicSpannerRpc.java:1596)
at com.google.cloud.spanner.SessionClient.internalBatchCreateSessions(SessionClient.java:303)
at com.google.cloud.spanner.SessionClient.access$000(SessionClient.java:38)
at com.google.cloud.spanner.SessionClient$BatchCreateSessionsRunnable.run(SessionClient.java:137)
... 7 more
Caused by: java.util.concurrent.ExecutionException: com.google.api.gax.rpc.UnavailableException: io.grpc.StatusRuntimeException: UNAVAILABLE: Credentials failed to obtain metadata
at com.google.common.util.concurrent.AbstractFuture.getDoneValue(AbstractFuture.java:588)
at com.google.common.util.concurrent.AbstractFuture.get(AbstractFuture.java:567)
at com.google.cloud.spanner.spi.v1.GapicSpannerRpc.get(GapicSpannerRpc.java:1877)
... 11 more
Caused by: com.google.api.gax.rpc.UnavailableException: io.grpc.StatusRuntimeException: UNAVAILABLE: Credentials failed to obtain metadata
at com.google.api.gax.rpc.ApiExceptionFactory.createException(ApiExceptionFactory.java:112)
at com.google.api.gax.rpc.ApiExceptionFactory.createException(ApiExceptionFactory.java:41)
at com.google.api.gax.grpc.GrpcApiExceptionFactory.create(GrpcApiExceptionFactory.java:86)
at com.google.api.gax.grpc.GrpcApiExceptionFactory.create(GrpcApiExceptionFactory.java:66)
at com.google.api.gax.grpc.GrpcExceptionCallable$ExceptionTransformingFuture.onFailure(GrpcExceptionCallable.java:97)
at com.google.api.core.ApiFutures$1.onFailure(ApiFutures.java:67)
at com.google.common.util.concurrent.Futures$CallbackListener.run(Futures.java:1132)
at com.google.common.util.concurrent.DirectExecutor.execute(DirectExecutor.java:31)
at com.google.common.util.concurrent.AbstractFuture.executeListener(AbstractFuture.java:1270)
at com.google.common.util.concurrent.AbstractFuture.complete(AbstractFuture.java:1038)
at com.google.common.util.concurrent.AbstractFuture.setException(AbstractFuture.java:808)
at io.grpc.stub.ClientCalls$GrpcFuture.setException(ClientCalls.java:574)
at io.grpc.stub.ClientCalls$UnaryStreamToFuture.onClose(ClientCalls.java:544)
at io.grpc.PartialForwardingClientCallListener.onClose(PartialForwardingClientCallListener.java:39)
at io.grpc.ForwardingClientCallListener.onClose(ForwardingClientCallListener.java:23)
at io.grpc.ForwardingClientCallListener$SimpleForwardingClientCallListener.onClose(ForwardingClientCallListener.java:40)
at com.google.api.gax.grpc.ChannelPool$ReleasingClientCall$1.onClose(ChannelPool.java:541)
at io.grpc.PartialForwardingClientCallListener.onClose(PartialForwardingClientCallListener.java:39)
at io.grpc.ForwardingClientCallListener.onClose(ForwardingClientCallListener.java:23)
at io.grpc.ForwardingClientCallListener$SimpleForwardingClientCallListener.onClose(ForwardingClientCallListener.java:40)
at io.grpc.PartialForwardingClientCallListener.onClose(PartialForwardingClientCallListener.java:39)
at io.grpc.ForwardingClientCallListener.onClose(ForwardingClientCallListener.java:23)
at io.grpc.ForwardingClientCallListener$SimpleForwardingClientCallListener.onClose(ForwardingClientCallListener.java:40)
at com.google.cloud.spanner.spi.v1.SpannerErrorInterceptor$1$1.onClose(SpannerErrorInterceptor.java:100)
at io.grpc.internal.ClientCallImpl.closeObserver(ClientCallImpl.java:576)
at io.grpc.internal.ClientCallImpl.access$300(ClientCallImpl.java:70)
at io.grpc.internal.ClientCallImpl$ClientStreamListenerImpl$1StreamClosed.runInternal(ClientCallImpl.java:757)
at io.grpc.internal.ClientCallImpl$ClientStreamListenerImpl$1StreamClosed.runInContext(ClientCallImpl.java:736)
at io.grpc.internal.ContextRunnable.run(ContextRunnable.java:37)
at io.grpc.internal.SerializingExecutor.run(SerializingExecutor.java:133)
... 7 more
Caused by: io.grpc.StatusRuntimeException: UNAVAILABLE: Credentials failed to obtain metadata
at io.grpc.Status.asRuntimeException(Status.java:539)
... 25 more
Caused by: com.google.auth.oauth2.GoogleAuthException: Error getting access token for service account: 400 Bad Request
POST https://oauth2.googleapis.com/token
{"error":"invalid_grant","error_description":"Invalid JWT Signature."}, iss: java-client-testing@span-cloud-testing.iam.gserviceaccount.com
at com.google.auth.oauth2.GoogleAuthException.createWithTokenEndpointResponseException(GoogleAuthException.java:131)
at com.google.auth.oauth2.ServiceAccountCredentials.refreshAccessToken(ServiceAccountCredentials.java:541)
at com.google.auth.oauth2.OAuth2Credentials$1.call(OAuth2Credentials.java:269)
at com.google.auth.oauth2.OAuth2Credentials$1.call(OAuth2Credentials.java:266)
at java.util.concurrent.FutureTask.run(FutureTask.java:266)
at com.google.auth.oauth2.OAuth2Credentials$RefreshTask.run(OAuth2Credentials.java:633)
... 3 more
Caused by: com.google.api.client.http.HttpResponseException: 400 Bad Request
POST https://oauth2.googleapis.com/token
{"error":"invalid_grant","error_description":"Invalid JWT Signature."}
at com.google.api.client.http.HttpResponseException$Builder.build(HttpResponseException.java:293)
at com.google.api.client.http.HttpRequest.execute(HttpRequest.java:1118)
at com.google.auth.oauth2.ServiceAccountCredentials.refreshAccessToken(ServiceAccountCredentials.java:538)
... 7 more
</pre></details> | non_design | spanner jdbc it itjdbcpgdatabasemetadatatest testgetexportedkeys failed note was also for this test but it was closed more than days ago so i didn t mark it flaky commit buildurl status failed test output com google cloud spanner spannerexception unavailable com google cloud spanner spannerexception unavailable com google api gax rpc unavailableexception io grpc statusruntimeexception unavailable credentials failed to obtain metadata at com google cloud spanner spannerexceptionfactory newspannerexceptionpreformatted spannerexceptionfactory java at com google cloud spanner spannerexceptionfactory newspannerexceptionpreformatted spannerexceptionfactory java at com google cloud spanner spannerexceptionfactory newspannerexception spannerexceptionfactory java at com google cloud spanner spannerexceptionfactory newspannerexception spannerexceptionfactory java at com google cloud spanner spannerexceptionfactory newspannerexception spannerexceptionfactory java at com google cloud spanner spannerexceptionfactory asspannerexception spannerexceptionfactory java at com google cloud spanner sessionpool getdialect sessionpool java at com google cloud spanner databaseclientimpl getdialect databaseclientimpl java at com google cloud spanner connection connectionimpl getdialect connectionimpl java at com google cloud spanner jdbc abstractjdbcconnection getdialect abstractjdbcconnection java at com google cloud spanner jdbc jdbcdatabasemetadata getexportedkeys jdbcdatabasemetadata java at com google cloud spanner jdbc it itjdbcpgdatabasemetadatatest testgetexportedkeys itjdbcpgdatabasemetadatatest java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org junit runners model frameworkmethod runreflectivecall frameworkmethod java at org junit internal runners model reflectivecallable run reflectivecallable java at org junit runners model frameworkmethod invokeexplosively frameworkmethod java at org junit internal runners statements invokemethod evaluate invokemethod java at org junit internal runners statements runbefores evaluate runbefores java at org junit runners parentrunner evaluate parentrunner java at org junit runners evaluate java at org junit runners parentrunner runleaf parentrunner java at org junit runners runchild java at org junit runners runchild java at org junit runners parentrunner run parentrunner java at org junit runners parentrunner schedule parentrunner java at org junit runners parentrunner runchildren parentrunner java at org junit runners parentrunner access parentrunner java at org junit runners parentrunner evaluate parentrunner java at org junit internal runners statements runbefores evaluate runbefores java at org junit rules externalresource evaluate externalresource java at org junit rules runrules evaluate runrules java at org junit runners parentrunner evaluate parentrunner java at org junit runners parentrunner run parentrunner java at org junit runners suite runchild suite java at org junit runners suite runchild suite java at org junit runners parentrunner run parentrunner java at org junit runners parentrunner schedule parentrunner java at org junit runners parentrunner runchildren parentrunner java at org junit runners parentrunner access parentrunner java at org junit runners parentrunner evaluate parentrunner java at org junit runners parentrunner evaluate parentrunner java at org junit runners parentrunner run parentrunner java at org apache maven surefire junitcore junitcore run junitcore java at org apache maven surefire junitcore junitcorewrapper createrequestandrun junitcorewrapper java at org apache maven surefire junitcore junitcorewrapper executelazy junitcorewrapper java at org apache maven surefire junitcore junitcorewrapper execute junitcorewrapper java at org apache maven surefire junitcore junitcorewrapper execute junitcorewrapper java at org apache maven surefire junitcore junitcoreprovider invoke junitcoreprovider java at org apache maven surefire booter forkedbooter runsuitesinprocess forkedbooter java at org apache maven surefire booter forkedbooter execute forkedbooter java at org apache maven surefire booter forkedbooter run forkedbooter java at org apache maven surefire booter forkedbooter main forkedbooter java caused by java util concurrent executionexception com google cloud spanner spannerexception unavailable com google api gax rpc unavailableexception io grpc statusruntimeexception unavailable credentials failed to obtain metadata at com google common util concurrent abstractfuture getdonevalue abstractfuture java at com google common util concurrent abstractfuture get abstractfuture java at com google common util concurrent abstractfuture trustedfuture get abstractfuture java at com google cloud spanner sessionpool getdialect sessionpool java more caused by com google cloud spanner spannerexception unavailable com google api gax rpc unavailableexception io grpc statusruntimeexception unavailable credentials failed to obtain metadata at com google cloud spanner spannerexceptionfactory newspannerexceptionpreformatted spannerexceptionfactory java at com google cloud spanner spannerexceptionfactory newspannerexceptionpreformatted spannerexceptionfactory java at com google cloud spanner spannerexceptionfactory newspannerexception spannerexceptionfactory java at com google cloud spanner spannerexceptionfactory newspannerexception spannerexceptionfactory java at com google cloud spanner sessionpool sessionconsumerimpl onsessioncreatefailure sessionpool java at com google cloud spanner sessionclient batchcreatesessionsrunnable run sessionclient java at java util concurrent executors runnableadapter call executors java at java util concurrent futuretask run futuretask java at java util concurrent scheduledthreadpoolexecutor scheduledfuturetask access scheduledthreadpoolexecutor java at java util concurrent scheduledthreadpoolexecutor scheduledfuturetask run scheduledthreadpoolexecutor java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java lang thread run thread java caused by com google cloud spanner spannerexception unavailable com google api gax rpc unavailableexception io grpc statusruntimeexception unavailable credentials failed to obtain metadata at com google cloud spanner spannerexceptionfactory newspannerexceptionpreformatted spannerexceptionfactory java at com google cloud spanner spannerexceptionfactory newspannerexceptionpreformatted spannerexceptionfactory java at com google cloud spanner spannerexceptionfactory newspannerexception spannerexceptionfactory java at com google cloud spanner spannerexceptionfactory newspannerexception spannerexceptionfactory java at com google cloud spanner spi gapicspannerrpc get gapicspannerrpc java at com google cloud spanner spi gapicspannerrpc batchcreatesessions gapicspannerrpc java at com google cloud spanner sessionclient internalbatchcreatesessions sessionclient java at com google cloud spanner sessionclient access sessionclient java at com google cloud spanner sessionclient batchcreatesessionsrunnable run sessionclient java more caused by java util concurrent executionexception com google api gax rpc unavailableexception io grpc statusruntimeexception unavailable credentials failed to obtain metadata at com google common util concurrent abstractfuture getdonevalue abstractfuture java at com google common util concurrent abstractfuture get abstractfuture java at com google cloud spanner spi gapicspannerrpc get gapicspannerrpc java more caused by com google api gax rpc unavailableexception io grpc statusruntimeexception unavailable credentials failed to obtain metadata at com google api gax rpc apiexceptionfactory createexception apiexceptionfactory java at com google api gax rpc apiexceptionfactory createexception apiexceptionfactory java at com google api gax grpc grpcapiexceptionfactory create grpcapiexceptionfactory java at com google api gax grpc grpcapiexceptionfactory create grpcapiexceptionfactory java at com google api gax grpc grpcexceptioncallable exceptiontransformingfuture onfailure grpcexceptioncallable java at com google api core apifutures onfailure apifutures java at com google common util concurrent futures callbacklistener run futures java at com google common util concurrent directexecutor execute directexecutor java at com google common util concurrent abstractfuture executelistener abstractfuture java at com google common util concurrent abstractfuture complete abstractfuture java at com google common util concurrent abstractfuture setexception abstractfuture java at io grpc stub clientcalls grpcfuture setexception clientcalls java at io grpc stub clientcalls unarystreamtofuture onclose clientcalls java at io grpc partialforwardingclientcalllistener onclose partialforwardingclientcalllistener java at io grpc forwardingclientcalllistener onclose forwardingclientcalllistener java at io grpc forwardingclientcalllistener simpleforwardingclientcalllistener onclose forwardingclientcalllistener java at com google api gax grpc channelpool releasingclientcall onclose channelpool java at io grpc partialforwardingclientcalllistener onclose partialforwardingclientcalllistener java at io grpc forwardingclientcalllistener onclose forwardingclientcalllistener java at io grpc forwardingclientcalllistener simpleforwardingclientcalllistener onclose forwardingclientcalllistener java at io grpc partialforwardingclientcalllistener onclose partialforwardingclientcalllistener java at io grpc forwardingclientcalllistener onclose forwardingclientcalllistener java at io grpc forwardingclientcalllistener simpleforwardingclientcalllistener onclose forwardingclientcalllistener java at com google cloud spanner spi spannererrorinterceptor onclose spannererrorinterceptor java at io grpc internal clientcallimpl closeobserver clientcallimpl java at io grpc internal clientcallimpl access clientcallimpl java at io grpc internal clientcallimpl clientstreamlistenerimpl runinternal clientcallimpl java at io grpc internal clientcallimpl clientstreamlistenerimpl runincontext clientcallimpl java at io grpc internal contextrunnable run contextrunnable java at io grpc internal serializingexecutor run serializingexecutor java more caused by io grpc statusruntimeexception unavailable credentials failed to obtain metadata at io grpc status asruntimeexception status java more caused by com google auth googleauthexception error getting access token for service account bad request post error invalid grant error description invalid jwt signature iss java client testing span cloud testing iam gserviceaccount com at com google auth googleauthexception createwithtokenendpointresponseexception googleauthexception java at com google auth serviceaccountcredentials refreshaccesstoken serviceaccountcredentials java at com google auth call java at com google auth call java at java util concurrent futuretask run futuretask java at com google auth refreshtask run java more caused by com google api client http httpresponseexception bad request post error invalid grant error description invalid jwt signature at com google api client http httpresponseexception builder build httpresponseexception java at com google api client http httprequest execute httprequest java at com google auth serviceaccountcredentials refreshaccesstoken serviceaccountcredentials java more | 0 |
58,636 | 3,090,219,287 | IssuesEvent | 2015-08-26 04:10:59 | AutomationSolutionz/Framework_0.1 | https://api.github.com/repos/AutomationSolutionz/Framework_0.1 | closed | bundle report is not taking the last result from the runs | bug Done Minar Priority 1 (Highest) Started | bundle report is not taking the last run result.
| 1.0 | bundle report is not taking the last result from the runs - bundle report is not taking the last run result.
| non_design | bundle report is not taking the last result from the runs bundle report is not taking the last run result | 0 |
42,307 | 10,958,766,079 | IssuesEvent | 2019-11-27 10:02:39 | cakephp/cakephp | https://api.github.com/repos/cakephp/cakephp | closed | 4.x - Controller integration testing mismatched tokens | defect testing | This is a (multiple allowed):
* [x] bug
* [ ] enhancement
* [ ] feature-discussion (RFC)
* CakePHP Version: 4.0.0-RC1
* Platform and Target: Nginx 1.17.3 & PHP 7.3.10
### What you did
I am trying to run an integration test on a controller method. My AppController implements both AuthComponent and SecurityComponent. I also have the CsrfMiddleware enabled in the routing.
My test case looks like the following. I have used `$this->session()` in the `setUp` to add Auth session data.
```php
/**
* Test add method
*
* @return void
* @throws \PHPUnit\Exception
* @throws \Throwable
*/
public function testAddWithInvalidCommentModel()
{
$this->expectException(\BadMethodCallException::class);
$this->expectExceptionMessage('Ye gads! What did you do?');
$this->enableCsrfToken();
$this->enableSecurityToken();
$this->setUnlockedFields(['comment']);
$this->post('/comments/add/invalid/999', ['comment' => 'Expecting an exception here']);
$this->assertResponseFailure();
}
```
The code snippet I am trying to test is the following,
```php
/**
* Add a new comment to either a Question or Answer
*
* @param string $model Name of the model being commented on, expected lowercase plural, eg, questions
* @param int|string $id Primary key of the item
* @return \Cake\Http\Response
*/
public function add(string $model, $id)
{
$className = Inflector::camelize($model);
$this->getRequest()->allowMethod('post');
if (!in_array($className, ['Questions', 'Answers'])) {
throw new \BadMethodCallException('Ye gads! What did you do?');
}
// Rest of method, etc
```
### What happened
Thanks to some help from @ADmad and @ndm2 in Slack, I added some methods to include the tokens in my request. However I still see an exception due to mismatched tokens.
`2019-11-21 16:11:48 Error: [Cake\Controller\Exception\AuthSecurityException] Invalid security debug token. in /Users/davidyell/Sites/Learning-CakePHP4/vendor/cakephp/cakephp/src/Controller/Component/SecurityComponent.php on line 245`
### What you expected to happen
I expected the`IntegrationTestTrait` to take care of the tokens for me, so that I could focus on testing my controller method.
### What's going on?
I am not sure, but my investigations have led me to think that the `fields` property is missing from the `_Token`. When I debug the data in `SecurityComponent::_validatePost` I can see the following.
Which are the json encoded `$hashParts`, `$check` and `$token`, as they appear in that method.
```
2019-11-21 16:11:48 Debug: ["\/comments\/add\/invalid\/999","a:0:{}","comment",""]
2019-11-21 16:11:48 Debug: 640dba12fdacfa1a216fd075110213e5b4155971
2019-11-21 16:11:48 Debug: da1283c6d02a43992eaf3b52b6b3f2276b6a1b6b
```
It's clear from this that the token mismatch is causing the request to fail, but I'm unsure why that might be, except for the `a:0:{}` empty `fields` which I tracked down through `_hashParts()` and into `_fieldsList()` methods.
For reference this code is available in my repository https://github.com/davidyell/Learning-CakePHP4 | 1.0 | 4.x - Controller integration testing mismatched tokens - This is a (multiple allowed):
* [x] bug
* [ ] enhancement
* [ ] feature-discussion (RFC)
* CakePHP Version: 4.0.0-RC1
* Platform and Target: Nginx 1.17.3 & PHP 7.3.10
### What you did
I am trying to run an integration test on a controller method. My AppController implements both AuthComponent and SecurityComponent. I also have the CsrfMiddleware enabled in the routing.
My test case looks like the following. I have used `$this->session()` in the `setUp` to add Auth session data.
```php
/**
* Test add method
*
* @return void
* @throws \PHPUnit\Exception
* @throws \Throwable
*/
public function testAddWithInvalidCommentModel()
{
$this->expectException(\BadMethodCallException::class);
$this->expectExceptionMessage('Ye gads! What did you do?');
$this->enableCsrfToken();
$this->enableSecurityToken();
$this->setUnlockedFields(['comment']);
$this->post('/comments/add/invalid/999', ['comment' => 'Expecting an exception here']);
$this->assertResponseFailure();
}
```
The code snippet I am trying to test is the following,
```php
/**
* Add a new comment to either a Question or Answer
*
* @param string $model Name of the model being commented on, expected lowercase plural, eg, questions
* @param int|string $id Primary key of the item
* @return \Cake\Http\Response
*/
public function add(string $model, $id)
{
$className = Inflector::camelize($model);
$this->getRequest()->allowMethod('post');
if (!in_array($className, ['Questions', 'Answers'])) {
throw new \BadMethodCallException('Ye gads! What did you do?');
}
// Rest of method, etc
```
### What happened
Thanks to some help from @ADmad and @ndm2 in Slack, I added some methods to include the tokens in my request. However I still see an exception due to mismatched tokens.
`2019-11-21 16:11:48 Error: [Cake\Controller\Exception\AuthSecurityException] Invalid security debug token. in /Users/davidyell/Sites/Learning-CakePHP4/vendor/cakephp/cakephp/src/Controller/Component/SecurityComponent.php on line 245`
### What you expected to happen
I expected the`IntegrationTestTrait` to take care of the tokens for me, so that I could focus on testing my controller method.
### What's going on?
I am not sure, but my investigations have led me to think that the `fields` property is missing from the `_Token`. When I debug the data in `SecurityComponent::_validatePost` I can see the following.
Which are the json encoded `$hashParts`, `$check` and `$token`, as they appear in that method.
```
2019-11-21 16:11:48 Debug: ["\/comments\/add\/invalid\/999","a:0:{}","comment",""]
2019-11-21 16:11:48 Debug: 640dba12fdacfa1a216fd075110213e5b4155971
2019-11-21 16:11:48 Debug: da1283c6d02a43992eaf3b52b6b3f2276b6a1b6b
```
It's clear from this that the token mismatch is causing the request to fail, but I'm unsure why that might be, except for the `a:0:{}` empty `fields` which I tracked down through `_hashParts()` and into `_fieldsList()` methods.
For reference this code is available in my repository https://github.com/davidyell/Learning-CakePHP4 | non_design | x controller integration testing mismatched tokens this is a multiple allowed bug enhancement feature discussion rfc cakephp version platform and target nginx php what you did i am trying to run an integration test on a controller method my appcontroller implements both authcomponent and securitycomponent i also have the csrfmiddleware enabled in the routing my test case looks like the following i have used this session in the setup to add auth session data php test add method return void throws phpunit exception throws throwable public function testaddwithinvalidcommentmodel this expectexception badmethodcallexception class this expectexceptionmessage ye gads what did you do this enablecsrftoken this enablesecuritytoken this setunlockedfields this post comments add invalid this assertresponsefailure the code snippet i am trying to test is the following php add a new comment to either a question or answer param string model name of the model being commented on expected lowercase plural eg questions param int string id primary key of the item return cake http response public function add string model id classname inflector camelize model this getrequest allowmethod post if in array classname throw new badmethodcallexception ye gads what did you do rest of method etc what happened thanks to some help from admad and in slack i added some methods to include the tokens in my request however i still see an exception due to mismatched tokens error invalid security debug token in users davidyell sites learning vendor cakephp cakephp src controller component securitycomponent php on line what you expected to happen i expected the integrationtesttrait to take care of the tokens for me so that i could focus on testing my controller method what s going on i am not sure but my investigations have led me to think that the fields property is missing from the token when i debug the data in securitycomponent validatepost i can see the following which are the json encoded hashparts check and token as they appear in that method debug debug debug it s clear from this that the token mismatch is causing the request to fail but i m unsure why that might be except for the a empty fields which i tracked down through hashparts and into fieldslist methods for reference this code is available in my repository | 0 |
621,936 | 19,600,796,964 | IssuesEvent | 2022-01-06 00:56:08 | azerothcore/azerothcore-wotlk | https://api.github.com/repos/azerothcore/azerothcore-wotlk | closed | Siltfin Murloc Population too high on Siltfin Shore (Azuremyst) | Confirmed 1-19 Priority-Low | <!-- IF YOU DO NOT FILL THIS TEMPLATE OUT, WE WILL CLOSE YOUR ISSUE! -->
<!-- This template is for problem reports, for feature suggestion etc... feel free to edit it.
If this is a crash report, upload the crashlog on https://gist.github.com/
For issues containing a fix, please create a Pull Request following this tutorial: http://www.azerothcore.org/wiki/Contribute#how-to-create-a-pull-request -->
<!-- WRITE A RELEVANT TITLE -->
Siltfin Murloc Population too high on Siltfin Shore (Azuremyst)
##### CURRENT BEHAVIOUR:
<!-- Describe the bug in detail. Database to link spells, NPCs, quests etc https://wowgaming.altervista.org/aowow/ -->
There are almost 100 Siltfins on the small beach which made doing the lvl 8 quest extremely hard for a group of two (Priest/Shaman) players. I couldn't imagine doing it alone as every pull pulls 2-5 murlocs.
https://www.wowhead.com/quest=9562/murlocs-why-here-why-now
##### EXPECTED BLIZZLIKE BEHAVIOUR:
<!-- Describe how it should be working without the bug. -->
Half the murlocs give or take.
https://www.youtube.com/watch?v=VCCVWUaPl2I
Video is from 2015 and people have been clearing the area but the difference is extreme.
##### STEPS TO REPRODUCE THE PROBLEM:
<!-- Describe precisely how to reproduce the bug so we can fix it or confirm its existence:
- Which commands to use? Which NPC to teleport to?
- Do we need to have debug flags on Cmake?
- Do we need to look at the console while the bug happens?
- Other steps
-->
1. Go to siltfin shore.
2. Observe the amount of murlocs
3. Cry
##### EXTRA NOTES:
<!--
Any information that can help the developers to identify and fix the issue should be put here.
Examples:
- was this bug always present in AzerothCore? if it was introduced after a change, please mention it
- the code line(s) that cause the issue
- does this feature work in other server appplications (e.g. CMaNGOS, TrinityCore, etc...) ?
-->
##### AC HASH/COMMIT:
<!-- IF YOU DO NOT FILL THIS OUT, WE WILL CLOSE YOUR ISSUE! NEVER WRITE "LATEST", ALWAYS PUT THE ACTUAL VALUE INSTEAD.
Find the commit hash (unique identifier) by running "git log" on your own clone of AzerothCore or by looking at here https://github.com/azerothcore/azerothcore-wotlk/commits/master -->
ChromieCraft
2020-12-31
6414b40 (chromiecraft)
##### OPERATING SYSTEM:
<!-- Windows 7/10, Debian 8/9/10, Ubuntu 16/18 etc... -->
ChromieCraft
##### MODULES:
<!-- Are you using modules? If yes, list them (note them down in a .txt for opening future issues) -->
ChromieCraft
##### OTHER CUSTOMIZATIONS:
<!-- Are you using any extra script?
- Did you apply any core patch/diff?
- Did you modify your database?
- Or do you have other customizations? If yes please specify them here.
-->
ChromieCraft
<!-- ------------------------- THE END ------------------------------
Thank you for your contribution.
If you use AzerothCore regularly, we really NEED your help to:
- TEST our fixes ( http://www.azerothcore.org/wiki/Contribute#how-to-test-a-pull-request )
- Report issues
- Improve the documentation/wiki
With your help the project can evolve much quicker!
-->
<!-- NOTE: If you intend to contribute more than once, you should really join us on our discord channel! We set cosmetic ranks for our contributors and may give access to special resources/knowledge to them! The link is on our site http://azerothcore.org/
-->
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/95701936-siltfin-murloc-population-too-high-on-siltfin-shore-azuremyst?utm_campaign=plugin&utm_content=tracker%2F40032087&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F40032087&utm_medium=issues&utm_source=github).
</bountysource-plugin> | 1.0 | Siltfin Murloc Population too high on Siltfin Shore (Azuremyst) - <!-- IF YOU DO NOT FILL THIS TEMPLATE OUT, WE WILL CLOSE YOUR ISSUE! -->
<!-- This template is for problem reports, for feature suggestion etc... feel free to edit it.
If this is a crash report, upload the crashlog on https://gist.github.com/
For issues containing a fix, please create a Pull Request following this tutorial: http://www.azerothcore.org/wiki/Contribute#how-to-create-a-pull-request -->
<!-- WRITE A RELEVANT TITLE -->
Siltfin Murloc Population too high on Siltfin Shore (Azuremyst)
##### CURRENT BEHAVIOUR:
<!-- Describe the bug in detail. Database to link spells, NPCs, quests etc https://wowgaming.altervista.org/aowow/ -->
There are almost 100 Siltfins on the small beach which made doing the lvl 8 quest extremely hard for a group of two (Priest/Shaman) players. I couldn't imagine doing it alone as every pull pulls 2-5 murlocs.
https://www.wowhead.com/quest=9562/murlocs-why-here-why-now
##### EXPECTED BLIZZLIKE BEHAVIOUR:
<!-- Describe how it should be working without the bug. -->
Half the murlocs give or take.
https://www.youtube.com/watch?v=VCCVWUaPl2I
Video is from 2015 and people have been clearing the area but the difference is extreme.
##### STEPS TO REPRODUCE THE PROBLEM:
<!-- Describe precisely how to reproduce the bug so we can fix it or confirm its existence:
- Which commands to use? Which NPC to teleport to?
- Do we need to have debug flags on Cmake?
- Do we need to look at the console while the bug happens?
- Other steps
-->
1. Go to siltfin shore.
2. Observe the amount of murlocs
3. Cry
##### EXTRA NOTES:
<!--
Any information that can help the developers to identify and fix the issue should be put here.
Examples:
- was this bug always present in AzerothCore? if it was introduced after a change, please mention it
- the code line(s) that cause the issue
- does this feature work in other server appplications (e.g. CMaNGOS, TrinityCore, etc...) ?
-->
##### AC HASH/COMMIT:
<!-- IF YOU DO NOT FILL THIS OUT, WE WILL CLOSE YOUR ISSUE! NEVER WRITE "LATEST", ALWAYS PUT THE ACTUAL VALUE INSTEAD.
Find the commit hash (unique identifier) by running "git log" on your own clone of AzerothCore or by looking at here https://github.com/azerothcore/azerothcore-wotlk/commits/master -->
ChromieCraft
2020-12-31
6414b40 (chromiecraft)
##### OPERATING SYSTEM:
<!-- Windows 7/10, Debian 8/9/10, Ubuntu 16/18 etc... -->
ChromieCraft
##### MODULES:
<!-- Are you using modules? If yes, list them (note them down in a .txt for opening future issues) -->
ChromieCraft
##### OTHER CUSTOMIZATIONS:
<!-- Are you using any extra script?
- Did you apply any core patch/diff?
- Did you modify your database?
- Or do you have other customizations? If yes please specify them here.
-->
ChromieCraft
<!-- ------------------------- THE END ------------------------------
Thank you for your contribution.
If you use AzerothCore regularly, we really NEED your help to:
- TEST our fixes ( http://www.azerothcore.org/wiki/Contribute#how-to-test-a-pull-request )
- Report issues
- Improve the documentation/wiki
With your help the project can evolve much quicker!
-->
<!-- NOTE: If you intend to contribute more than once, you should really join us on our discord channel! We set cosmetic ranks for our contributors and may give access to special resources/knowledge to them! The link is on our site http://azerothcore.org/
-->
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/95701936-siltfin-murloc-population-too-high-on-siltfin-shore-azuremyst?utm_campaign=plugin&utm_content=tracker%2F40032087&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F40032087&utm_medium=issues&utm_source=github).
</bountysource-plugin> | non_design | siltfin murloc population too high on siltfin shore azuremyst this template is for problem reports for feature suggestion etc feel free to edit it if this is a crash report upload the crashlog on for issues containing a fix please create a pull request following this tutorial siltfin murloc population too high on siltfin shore azuremyst current behaviour there are almost siltfins on the small beach which made doing the lvl quest extremely hard for a group of two priest shaman players i couldn t imagine doing it alone as every pull pulls murlocs expected blizzlike behaviour half the murlocs give or take video is from and people have been clearing the area but the difference is extreme steps to reproduce the problem describe precisely how to reproduce the bug so we can fix it or confirm its existence which commands to use which npc to teleport to do we need to have debug flags on cmake do we need to look at the console while the bug happens other steps go to siltfin shore observe the amount of murlocs cry extra notes any information that can help the developers to identify and fix the issue should be put here examples was this bug always present in azerothcore if it was introduced after a change please mention it the code line s that cause the issue does this feature work in other server appplications e g cmangos trinitycore etc ac hash commit if you do not fill this out we will close your issue never write latest always put the actual value instead find the commit hash unique identifier by running git log on your own clone of azerothcore or by looking at here chromiecraft chromiecraft operating system chromiecraft modules chromiecraft other customizations are you using any extra script did you apply any core patch diff did you modify your database or do you have other customizations if yes please specify them here chromiecraft the end thank you for your contribution if you use azerothcore regularly we really need your help to test our fixes report issues improve the documentation wiki with your help the project can evolve much quicker note if you intend to contribute more than once you should really join us on our discord channel we set cosmetic ranks for our contributors and may give access to special resources knowledge to them the link is on our site want to back this issue we accept bounties via | 0 |
123,364 | 16,485,887,284 | IssuesEvent | 2021-05-24 17:53:48 | carbon-design-system/carbon-for-ibm-dotcom | https://api.github.com/repos/carbon-design-system/carbon-for-ibm-dotcom | closed | [Filter panel] Design support of the a/b testing by the ibm.com search team | Airtable Done design design: research | <!-- Avoid any type of solutions in this user story -->
<!-- replace _{{...}}_ with your own words or remove -->
#### User Story
<!-- {{Provide a detailed description of the user's need here, but avoid any type of solutions}} -->
> As a `[user role below]`:
DDS designer
> I need to:
provide a/b testing consulting support to the ibm.com Search team
> so that I can:
have the metrics to refine / improve the filter panel designs
#### Additional information
<!-- {{Please provide any additional information or resources for reference}} -->
- ibm.com Search Offering Manager: Dave McDuff
#### Acceptance criteria
- [x] Meet with the ibm.com Search squad, as needed
- [ ] _{{State another}}_
- [ ] _{{And another}}_
<!-- Consider the following when writing Acceptance criteria for this story. -->
<!-- *** Each product backlog item or user story should have at least one Acceptance criteria. -->
<!-- *** Acceptance criteria defines a deliverable that can be completed in a single sprint -->
<!-- *** Each Acceptance criterion is independently testable. -->
<!-- *** Include functional as well as non-functional criteria – when relevant. -->
<!-- *** Team members write Acceptance criteria and the Product Owner verifies it. -->
| 2.0 | [Filter panel] Design support of the a/b testing by the ibm.com search team - <!-- Avoid any type of solutions in this user story -->
<!-- replace _{{...}}_ with your own words or remove -->
#### User Story
<!-- {{Provide a detailed description of the user's need here, but avoid any type of solutions}} -->
> As a `[user role below]`:
DDS designer
> I need to:
provide a/b testing consulting support to the ibm.com Search team
> so that I can:
have the metrics to refine / improve the filter panel designs
#### Additional information
<!-- {{Please provide any additional information or resources for reference}} -->
- ibm.com Search Offering Manager: Dave McDuff
#### Acceptance criteria
- [x] Meet with the ibm.com Search squad, as needed
- [ ] _{{State another}}_
- [ ] _{{And another}}_
<!-- Consider the following when writing Acceptance criteria for this story. -->
<!-- *** Each product backlog item or user story should have at least one Acceptance criteria. -->
<!-- *** Acceptance criteria defines a deliverable that can be completed in a single sprint -->
<!-- *** Each Acceptance criterion is independently testable. -->
<!-- *** Include functional as well as non-functional criteria – when relevant. -->
<!-- *** Team members write Acceptance criteria and the Product Owner verifies it. -->
| design | design support of the a b testing by the ibm com search team user story as a dds designer i need to provide a b testing consulting support to the ibm com search team so that i can have the metrics to refine improve the filter panel designs additional information ibm com search offering manager dave mcduff acceptance criteria meet with the ibm com search squad as needed state another and another | 1 |
692,494 | 23,737,068,501 | IssuesEvent | 2022-08-31 09:02:33 | lowRISC/opentitan | https://api.github.com/repos/lowRISC/opentitan | closed | [ci] CW310 test failures are ignored - false positive | Priority:P0 Type:Bug Component:CI SW:ROM | Please see the [cw310 tests log](https://dev.azure.com/lowrisc/4c50229e-f6cb-4f39-8522-585bb3841438/_apis/build/builds/92369/logs/200) of fe8a53a299d244d254b4a80eb83d8747d4c046a4:
```
2022-08-31T00:26:31.2909692Z Executed 179 out of 179 tests: 172 tests pass and 7 fail locally.
2022-08-31T00:26:31.2943205Z
2022-08-31T00:26:31.2944353Z (00:26:31) INFO: Build completed, 7 tests FAILED, 3570 total actions
2022-08-31T00:26:31.3021220Z + python3 ./util/fpga/cw310_reboot.py
2022-08-31T00:26:31.4598862Z Found CW310 with FW Version: 0.40.1
2022-08-31T00:26:31.4752410Z To reproduce failures locally, follow the instructions at https://docs.opentitan.org/doc/getting_started/setup_fpga/#reproducing-fpga-ci-failures-locally
2022-08-31T00:26:31.4815181Z ##[section]Finishing: Execute tests
```
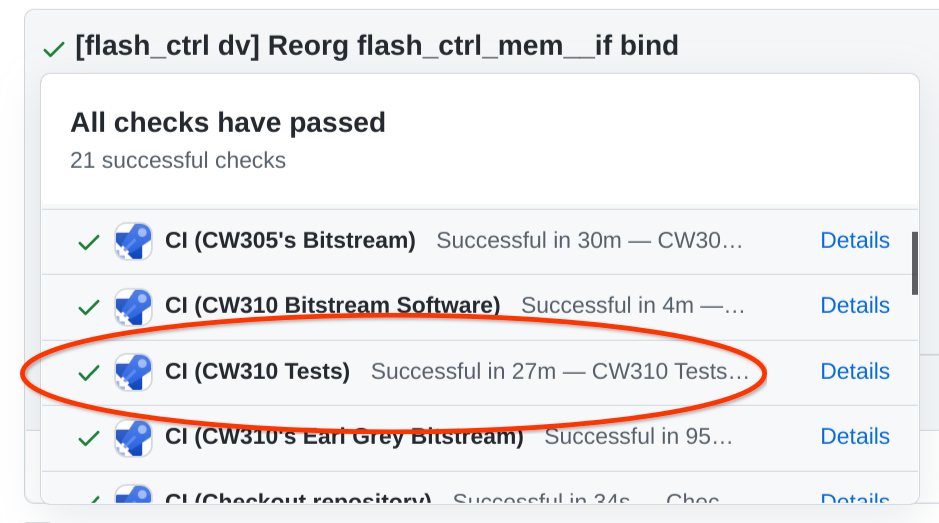
| 1.0 | [ci] CW310 test failures are ignored - false positive - Please see the [cw310 tests log](https://dev.azure.com/lowrisc/4c50229e-f6cb-4f39-8522-585bb3841438/_apis/build/builds/92369/logs/200) of fe8a53a299d244d254b4a80eb83d8747d4c046a4:
```
2022-08-31T00:26:31.2909692Z Executed 179 out of 179 tests: 172 tests pass and 7 fail locally.
2022-08-31T00:26:31.2943205Z
2022-08-31T00:26:31.2944353Z (00:26:31) INFO: Build completed, 7 tests FAILED, 3570 total actions
2022-08-31T00:26:31.3021220Z + python3 ./util/fpga/cw310_reboot.py
2022-08-31T00:26:31.4598862Z Found CW310 with FW Version: 0.40.1
2022-08-31T00:26:31.4752410Z To reproduce failures locally, follow the instructions at https://docs.opentitan.org/doc/getting_started/setup_fpga/#reproducing-fpga-ci-failures-locally
2022-08-31T00:26:31.4815181Z ##[section]Finishing: Execute tests
```
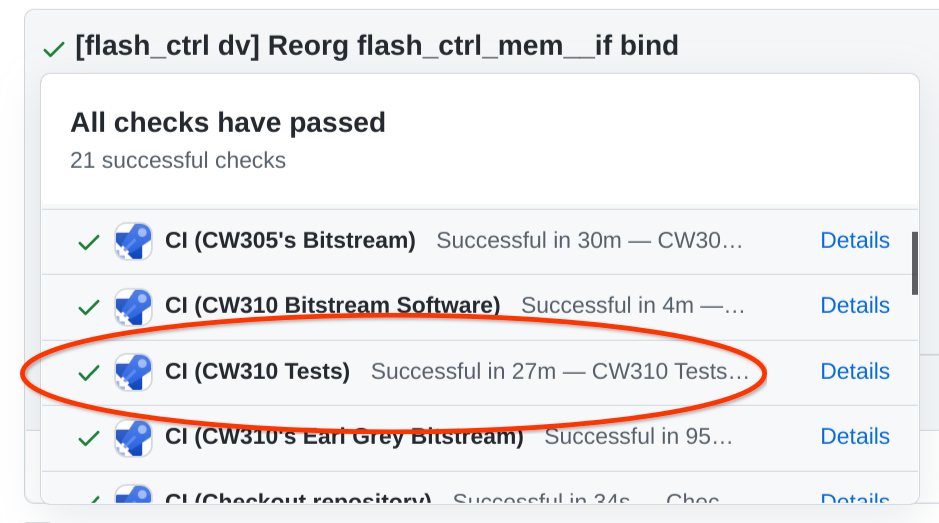
| non_design | test failures are ignored false positive please see the of executed out of tests tests pass and fail locally info build completed tests failed total actions util fpga reboot py found with fw version to reproduce failures locally follow the instructions at finishing execute tests | 0 |
28,324 | 4,098,287,629 | IssuesEvent | 2016-06-03 07:39:39 | brave/browser-laptop | https://api.github.com/repos/brave/browser-laptop | reopened | browserWindow has no icon | design | browserWindow needs an icon for brave to show an icon on Ubuntu or you get a grey icon:

This should be added here: https://github.com/brave/browser-laptop/blob/75c788aeb00b82957b7be58473332df5da13ac80/js/stores/appStore.js#L111 and it should be a png. | 1.0 | browserWindow has no icon - browserWindow needs an icon for brave to show an icon on Ubuntu or you get a grey icon:

This should be added here: https://github.com/brave/browser-laptop/blob/75c788aeb00b82957b7be58473332df5da13ac80/js/stores/appStore.js#L111 and it should be a png. | design | browserwindow has no icon browserwindow needs an icon for brave to show an icon on ubuntu or you get a grey icon this should be added here and it should be a png | 1 |
306,590 | 23,165,586,249 | IssuesEvent | 2022-07-30 00:10:39 | Soontao/cds-mysql | https://api.github.com/repos/Soontao/cds-mysql | closed | [FEATURE REQUEST] support partition | documentation enhancement | **Is your feature request related to a problem? Please describe.**
A clear and concise description of what the problem is. Ex. I'm always frustrated when [...]
**Describe the solution you'd like**
A clear and concise description of what you want to happen.
**Describe alternatives you've considered**
A clear and concise description of any alternative solutions or features you've considered.
**Additional context**
Add any other context or screenshots about the feature request here.
| 1.0 | [FEATURE REQUEST] support partition - **Is your feature request related to a problem? Please describe.**
A clear and concise description of what the problem is. Ex. I'm always frustrated when [...]
**Describe the solution you'd like**
A clear and concise description of what you want to happen.
**Describe alternatives you've considered**
A clear and concise description of any alternative solutions or features you've considered.
**Additional context**
Add any other context or screenshots about the feature request here.
| non_design | support partition is your feature request related to a problem please describe a clear and concise description of what the problem is ex i m always frustrated when describe the solution you d like a clear and concise description of what you want to happen describe alternatives you ve considered a clear and concise description of any alternative solutions or features you ve considered additional context add any other context or screenshots about the feature request here | 0 |
91,042 | 18,289,820,266 | IssuesEvent | 2021-10-05 14:11:16 | hardkoded/puppeteer-sharp | https://api.github.com/repos/hardkoded/puppeteer-sharp | closed | Add missing tests input.spec.ts | puppeteer code | input.spec.ts: FileChooser.accept: should fail for non-existent files | 1.0 | Add missing tests input.spec.ts - input.spec.ts: FileChooser.accept: should fail for non-existent files | non_design | add missing tests input spec ts input spec ts filechooser accept should fail for non existent files | 0 |
174,267 | 27,610,007,191 | IssuesEvent | 2023-03-09 15:23:34 | RRZE-Webteam/FAU-Einrichtungen | https://api.github.com/repos/RRZE-Webteam/FAU-Einrichtungen | opened | Hauptmenü Farbgebung – Der Hover nutzt die Aktive Farbe | Diskussion Design Prüfen | Wieder mal was zu prüfen / diskutieren
Aktuell ist beim Hover der Menüpunkte zu sehen, dass diese im aktiven Blau hinterlegt sind.
Die Buttons sind beim Hover in einem dunkleren FAU-Blauton gehalten.
Es sollte (in Rücksprache mit Silke) einheitlich sein.
Der Hover müsste also eigentlich ebenfalls das dunklere Blau nutzen, wenn Silke und ich das richtig gesehen haben.
Side by side. Hover-Element nutzt die gleiche Farbe wie der Standard-Button.
<img width="1509" alt="Bildschirmfoto 2023-03-09 um 16 22 39" src="https://user-images.githubusercontent.com/58593037/224070351-cefffc98-176c-4fe6-9b0c-65d21665e8d4.png">
| 1.0 | Hauptmenü Farbgebung – Der Hover nutzt die Aktive Farbe - Wieder mal was zu prüfen / diskutieren
Aktuell ist beim Hover der Menüpunkte zu sehen, dass diese im aktiven Blau hinterlegt sind.
Die Buttons sind beim Hover in einem dunkleren FAU-Blauton gehalten.
Es sollte (in Rücksprache mit Silke) einheitlich sein.
Der Hover müsste also eigentlich ebenfalls das dunklere Blau nutzen, wenn Silke und ich das richtig gesehen haben.
Side by side. Hover-Element nutzt die gleiche Farbe wie der Standard-Button.
<img width="1509" alt="Bildschirmfoto 2023-03-09 um 16 22 39" src="https://user-images.githubusercontent.com/58593037/224070351-cefffc98-176c-4fe6-9b0c-65d21665e8d4.png">
| design | hauptmenü farbgebung – der hover nutzt die aktive farbe wieder mal was zu prüfen diskutieren aktuell ist beim hover der menüpunkte zu sehen dass diese im aktiven blau hinterlegt sind die buttons sind beim hover in einem dunkleren fau blauton gehalten es sollte in rücksprache mit silke einheitlich sein der hover müsste also eigentlich ebenfalls das dunklere blau nutzen wenn silke und ich das richtig gesehen haben side by side hover element nutzt die gleiche farbe wie der standard button img width alt bildschirmfoto um src | 1 |
593,020 | 17,936,122,207 | IssuesEvent | 2021-09-10 15:31:45 | googleapis/google-cloud-dotnet | https://api.github.com/repos/googleapis/google-cloud-dotnet | closed | TailLogEntries crashes every hour | type: question api: logging priority: p2 | I understand that `TailLogEntries` is pre-GA, but maybe it will help.
#### Environment details
- OS: Ubuntu 20.04
- .NET version: 5.0.9
- Package name and version: Google.Cloud.Logging.V2 3.4.0
#### Steps to reproduce
Code:
```cs
LoggingServiceV2Client client = await _gcpLoggingClientBuilder.BuildAsync(ct);
CallSettings callsettings = CallSettings.FromExpiration(Expiration.None);
LoggingServiceV2Client.TailLogEntriesStream response = client.TailLogEntries(callsettings);
ct.Register(async () => await response.WriteCompleteAsync());
Task responseHandlerTask = Task.Run(async () =>
{
AsyncResponseStream<TailLogEntriesResponse> responseStream = response.GetResponseStream();
await foreach (TailLogEntriesResponse responseItem in responseStream)
{
for (int i = 0; i < responseItem.Entries.Count; i++)
{
LogEntry entry = responseItem.Entries[i];
await SendMessageAsync(entry, ct);
}
}
}, CancellationToken.None);
TailLogEntriesRequest request = new()
{
ResourceNames = { _resourceName },
Filter = _filter
};
await response.WriteAsync(request);
await responseHandlerTask;
```
`foreach` over `responseStream` fails every hour with:
`Grpc.Core.RpcException: Status(StatusCode="Unavailable", Detail="The service is currently unavailable."`
`Grpc.Core.RpcException: Status(StatusCode="Unavailable", Detail="Connection reset by peer"`
Without `CallSettings callsettings = CallSettings.FromExpiration(Expiration.None);` the error was
`Grpc.Core.RpcException: Status(StatusCode="DeadlineExceeded", Detail="Deadline Exceeded"`
UPD: Recently found that service just stopped receiving responses without any error
UPD: FYI we are doing `strip --strip-debug libgrpc_csharp_ext.x64.so` for builds, because this file is very huge. Could it be the reason? I think this is connected with #4813 | 1.0 | TailLogEntries crashes every hour - I understand that `TailLogEntries` is pre-GA, but maybe it will help.
#### Environment details
- OS: Ubuntu 20.04
- .NET version: 5.0.9
- Package name and version: Google.Cloud.Logging.V2 3.4.0
#### Steps to reproduce
Code:
```cs
LoggingServiceV2Client client = await _gcpLoggingClientBuilder.BuildAsync(ct);
CallSettings callsettings = CallSettings.FromExpiration(Expiration.None);
LoggingServiceV2Client.TailLogEntriesStream response = client.TailLogEntries(callsettings);
ct.Register(async () => await response.WriteCompleteAsync());
Task responseHandlerTask = Task.Run(async () =>
{
AsyncResponseStream<TailLogEntriesResponse> responseStream = response.GetResponseStream();
await foreach (TailLogEntriesResponse responseItem in responseStream)
{
for (int i = 0; i < responseItem.Entries.Count; i++)
{
LogEntry entry = responseItem.Entries[i];
await SendMessageAsync(entry, ct);
}
}
}, CancellationToken.None);
TailLogEntriesRequest request = new()
{
ResourceNames = { _resourceName },
Filter = _filter
};
await response.WriteAsync(request);
await responseHandlerTask;
```
`foreach` over `responseStream` fails every hour with:
`Grpc.Core.RpcException: Status(StatusCode="Unavailable", Detail="The service is currently unavailable."`
`Grpc.Core.RpcException: Status(StatusCode="Unavailable", Detail="Connection reset by peer"`
Without `CallSettings callsettings = CallSettings.FromExpiration(Expiration.None);` the error was
`Grpc.Core.RpcException: Status(StatusCode="DeadlineExceeded", Detail="Deadline Exceeded"`
UPD: Recently found that service just stopped receiving responses without any error
UPD: FYI we are doing `strip --strip-debug libgrpc_csharp_ext.x64.so` for builds, because this file is very huge. Could it be the reason? I think this is connected with #4813 | non_design | taillogentries crashes every hour i understand that taillogentries is pre ga but maybe it will help environment details os ubuntu net version package name and version google cloud logging steps to reproduce code cs client await gcploggingclientbuilder buildasync ct callsettings callsettings callsettings fromexpiration expiration none taillogentriesstream response client taillogentries callsettings ct register async await response writecompleteasync task responsehandlertask task run async asyncresponsestream responsestream response getresponsestream await foreach taillogentriesresponse responseitem in responsestream for int i i responseitem entries count i logentry entry responseitem entries await sendmessageasync entry ct cancellationtoken none taillogentriesrequest request new resourcenames resourcename filter filter await response writeasync request await responsehandlertask foreach over responsestream fails every hour with grpc core rpcexception status statuscode unavailable detail the service is currently unavailable grpc core rpcexception status statuscode unavailable detail connection reset by peer without callsettings callsettings callsettings fromexpiration expiration none the error was grpc core rpcexception status statuscode deadlineexceeded detail deadline exceeded upd recently found that service just stopped receiving responses without any error upd fyi we are doing strip strip debug libgrpc csharp ext so for builds because this file is very huge could it be the reason i think this is connected with | 0 |
24,076 | 3,881,245,168 | IssuesEvent | 2016-04-13 02:57:37 | department-of-veterans-affairs/veterans-employment-center | https://api.github.com/repos/department-of-veterans-affairs/veterans-employment-center | opened | text wrap looks off on C&E page | design | @gnakm is the text on this page supposed to wrap like this? it's only going partially across the page.

| 1.0 | text wrap looks off on C&E page - @gnakm is the text on this page supposed to wrap like this? it's only going partially across the page.

| design | text wrap looks off on c e page gnakm is the text on this page supposed to wrap like this it s only going partially across the page | 1 |
49,041 | 13,185,204,085 | IssuesEvent | 2020-08-12 20:55:55 | icecube-trac/tix3 | https://api.github.com/repos/icecube-trac/tix3 | opened | Doxygen docs generation is broken (Trac #642) | Incomplete Migration Migrated from Trac defect documentation | <details>
<summary><em>Migrated from https://code.icecube.wisc.edu/ticket/642
, reported by nega and owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2014-10-03T18:23:33",
"description": "Duplicate of #282",
"reporter": "nega",
"cc": "",
"resolution": "duplicate",
"_ts": "1412360613040634",
"component": "documentation",
"summary": "Doxygen docs generation is broken",
"priority": "normal",
"keywords": "",
"time": "2011-06-13T03:43:27",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
| 1.0 | Doxygen docs generation is broken (Trac #642) - <details>
<summary><em>Migrated from https://code.icecube.wisc.edu/ticket/642
, reported by nega and owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2014-10-03T18:23:33",
"description": "Duplicate of #282",
"reporter": "nega",
"cc": "",
"resolution": "duplicate",
"_ts": "1412360613040634",
"component": "documentation",
"summary": "Doxygen docs generation is broken",
"priority": "normal",
"keywords": "",
"time": "2011-06-13T03:43:27",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
| non_design | doxygen docs generation is broken trac migrated from reported by nega and owned by nega json status closed changetime description duplicate of reporter nega cc resolution duplicate ts component documentation summary doxygen docs generation is broken priority normal keywords time milestone owner nega type defect | 0 |
124,186 | 16,593,514,591 | IssuesEvent | 2021-06-01 10:37:51 | ThreeSixtyGiving/grantnav | https://api.github.com/repos/ThreeSixtyGiving/grantnav | closed | Search results - gap between "filters applied" and stats box is too small | Low Priority for March Launch issue needs clarification new design | 
Inserting `<div class="spacer-3"></div>` before the filter panel seems to work. | 1.0 | Search results - gap between "filters applied" and stats box is too small - 
Inserting `<div class="spacer-3"></div>` before the filter panel seems to work. | design | search results gap between filters applied and stats box is too small inserting before the filter panel seems to work | 1 |
109,686 | 11,647,672,057 | IssuesEvent | 2020-03-01 16:24:50 | universal-ctags/ctags | https://api.github.com/repos/universal-ctags/ctags | closed | docs: write about pattern truncation | Documentation Incompatibilities | I introduced code truncating a pattern for handling too long input line.
I should wirte about it to docs/format.rst.
| 1.0 | docs: write about pattern truncation - I introduced code truncating a pattern for handling too long input line.
I should wirte about it to docs/format.rst.
| non_design | docs write about pattern truncation i introduced code truncating a pattern for handling too long input line i should wirte about it to docs format rst | 0 |
87,817 | 10,968,616,525 | IssuesEvent | 2019-11-28 12:03:24 | statsmodels/statsmodels | https://api.github.com/repos/statsmodels/statsmodels | closed | KDEUnivariate bug with data at only one point | comp-nonparametric corner-case design | If a `KDEUnivariate` object is created with points only at one location it causes the density to be evaluated to `nan`. See this gist: https://gist.github.com/Padarn/2641c248e5f0a3bc7c3d
This is because the `bw` parameter is set to zero.
EDIT: Perhaps `bandwidths.py` should just default to `1` if `_select_sigma(X)=0`?
| 1.0 | KDEUnivariate bug with data at only one point - If a `KDEUnivariate` object is created with points only at one location it causes the density to be evaluated to `nan`. See this gist: https://gist.github.com/Padarn/2641c248e5f0a3bc7c3d
This is because the `bw` parameter is set to zero.
EDIT: Perhaps `bandwidths.py` should just default to `1` if `_select_sigma(X)=0`?
| design | kdeunivariate bug with data at only one point if a kdeunivariate object is created with points only at one location it causes the density to be evaluated to nan see this gist this is because the bw parameter is set to zero edit perhaps bandwidths py should just default to if select sigma x | 1 |
6,567 | 4,346,747,666 | IssuesEvent | 2016-07-29 17:03:20 | bocoup/skillsbot | https://api.github.com/repos/bocoup/skillsbot | closed | Rename “for” command to “user" and test | usability |
(eg. “user @cowboy” to see Ben’s skills)
This issue came out of usability testing. Many participants were unable to differentiate between the "for" and "find" commands.
| True | Rename “for” command to “user" and test -
(eg. “user @cowboy” to see Ben’s skills)
This issue came out of usability testing. Many participants were unable to differentiate between the "for" and "find" commands.
| non_design | rename “for” command to “user and test eg “user cowboy” to see ben’s skills this issue came out of usability testing many participants were unable to differentiate between the for and find commands | 0 |
144,042 | 5,534,769,016 | IssuesEvent | 2017-03-21 16:01:28 | Cadasta/cadasta-platform | https://api.github.com/repos/Cadasta/cadasta-platform | reopened | AssertionError at /api/v1/users/<user-name>/ | bug priority: low | ### Steps to reproduce the error
- Login with superuser (ex: 'iross' on local development server)
- visit /api/v1/users/**user-name**/
### Actual behavior
- AssertionError :
>Expected view UserAdminDetail to be called with a URL keyword argument named "username". Fix your URL conf, or set the `.lookup_field` attribute on the view correctly.
### Expected behavior
According to Docs [link](https://devwiki.corp.cadasta.org/User%20management%20API#get-a-single-user) superuser should be able to see specific user's details (ex: first_name, last_name, email ) and should be able to update them. | 1.0 | AssertionError at /api/v1/users/<user-name>/ - ### Steps to reproduce the error
- Login with superuser (ex: 'iross' on local development server)
- visit /api/v1/users/**user-name**/
### Actual behavior
- AssertionError :
>Expected view UserAdminDetail to be called with a URL keyword argument named "username". Fix your URL conf, or set the `.lookup_field` attribute on the view correctly.
### Expected behavior
According to Docs [link](https://devwiki.corp.cadasta.org/User%20management%20API#get-a-single-user) superuser should be able to see specific user's details (ex: first_name, last_name, email ) and should be able to update them. | non_design | assertionerror at api users steps to reproduce the error login with superuser ex iross on local development server visit api users user name actual behavior assertionerror expected view useradmindetail to be called with a url keyword argument named username fix your url conf or set the lookup field attribute on the view correctly expected behavior according to docs superuser should be able to see specific user s details ex first name last name email and should be able to update them | 0 |
160,402 | 25,158,241,917 | IssuesEvent | 2022-11-10 15:00:48 | mapasculturais/mapasculturais | https://api.github.com/repos/mapasculturais/mapasculturais | opened | [Redesign] Telas do Cadastro Único no Base V2 | Design / UX Modernização da Interface | Telas dos Agentes: Definir local dos campos do Cadastro Único e a Carteira do Cadastro Único da Cultura (Cartão de Visita) | 1.0 | [Redesign] Telas do Cadastro Único no Base V2 - Telas dos Agentes: Definir local dos campos do Cadastro Único e a Carteira do Cadastro Único da Cultura (Cartão de Visita) | design | telas do cadastro único no base telas dos agentes definir local dos campos do cadastro único e a carteira do cadastro único da cultura cartão de visita | 1 |
88,960 | 11,184,066,654 | IssuesEvent | 2019-12-31 16:16:01 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | closed | Form Requirements Inventory | design discovery documentation vsa-benefits-2 | ## User Story or Problem Statement
As a UX designer, I need to create a form requirements inventory so I can have a document containing all the required pieces for VA form 2345 (prosthetic socks) and VA form 2346 (hearing aid batteries).
## Task
- [x] Create a list end points items. (base requirements)
- [x] meet with design team a review similar items from each order method.
- [x] GH list
- [ ] share with DLC
## Goal
_A document containing an inventory of both VA form 2345 and 2346_
## Objectives or Key Results this is meant to further
- _Ensures that all required pieces are included in the form's design_
## Acceptance Criteria
- [x] _Create a document (most likely a Mural) containing an inventory for VA form 2345 & 2346_
- [x] _Share document with development team_
- [x] _Share the document's link in the comments section of this ticket_
| 1.0 | Form Requirements Inventory - ## User Story or Problem Statement
As a UX designer, I need to create a form requirements inventory so I can have a document containing all the required pieces for VA form 2345 (prosthetic socks) and VA form 2346 (hearing aid batteries).
## Task
- [x] Create a list end points items. (base requirements)
- [x] meet with design team a review similar items from each order method.
- [x] GH list
- [ ] share with DLC
## Goal
_A document containing an inventory of both VA form 2345 and 2346_
## Objectives or Key Results this is meant to further
- _Ensures that all required pieces are included in the form's design_
## Acceptance Criteria
- [x] _Create a document (most likely a Mural) containing an inventory for VA form 2345 & 2346_
- [x] _Share document with development team_
- [x] _Share the document's link in the comments section of this ticket_
| design | form requirements inventory user story or problem statement as a ux designer i need to create a form requirements inventory so i can have a document containing all the required pieces for va form prosthetic socks and va form hearing aid batteries task create a list end points items base requirements meet with design team a review similar items from each order method gh list share with dlc goal a document containing an inventory of both va form and objectives or key results this is meant to further ensures that all required pieces are included in the form s design acceptance criteria create a document most likely a mural containing an inventory for va form share document with development team share the document s link in the comments section of this ticket | 1 |
446,642 | 31,551,849,424 | IssuesEvent | 2023-09-02 06:26:31 | bazelbuild/bazel | https://api.github.com/repos/bazelbuild/bazel | opened | Add a note in the 'Distribution file directories' | type: documentation (cleanup) untriaged team-Documentation | ### Page link:
https://bazel.build/run/build#running-bazel-in-an-airgapped-environment
### Problem description (include actual vs expected text, if applicable):
It took me a while to understand that the the tar files need to be located in the directory uncompressed. I would be nice to just add a little note or an an example, e.g. (I was using the cpp-tuturial and had to include this to make it work)
$HOME/bazel/repos
|----- rules_cc-0.0.2.tar.gz
|----- bazelci_rules-1.0.0.tar.gz
bazel run --distdir=$HOME/bazel/repos //main:hello-world
### Where do you see this issue? (include link to specific section of the page, if applicable)
It is not really an issue, just make the documentation a bit clearer
### Any other information you'd like to share?
This entry on stackoverflow put me on the right track
https://stackoverflow.com/questions/67077183/bazel-build-air-gapped | 2.0 | Add a note in the 'Distribution file directories' - ### Page link:
https://bazel.build/run/build#running-bazel-in-an-airgapped-environment
### Problem description (include actual vs expected text, if applicable):
It took me a while to understand that the the tar files need to be located in the directory uncompressed. I would be nice to just add a little note or an an example, e.g. (I was using the cpp-tuturial and had to include this to make it work)
$HOME/bazel/repos
|----- rules_cc-0.0.2.tar.gz
|----- bazelci_rules-1.0.0.tar.gz
bazel run --distdir=$HOME/bazel/repos //main:hello-world
### Where do you see this issue? (include link to specific section of the page, if applicable)
It is not really an issue, just make the documentation a bit clearer
### Any other information you'd like to share?
This entry on stackoverflow put me on the right track
https://stackoverflow.com/questions/67077183/bazel-build-air-gapped | non_design | add a note in the distribution file directories page link problem description include actual vs expected text if applicable it took me a while to understand that the the tar files need to be located in the directory uncompressed i would be nice to just add a little note or an an example e g i was using the cpp tuturial and had to include this to make it work home bazel repos rules cc tar gz bazelci rules tar gz bazel run distdir home bazel repos main hello world where do you see this issue include link to specific section of the page if applicable it is not really an issue just make the documentation a bit clearer any other information you d like to share this entry on stackoverflow put me on the right track | 0 |
15,118 | 8,773,432,312 | IssuesEvent | 2018-12-18 16:50:57 | tensorflow/tensorflow | https://api.github.com/repos/tensorflow/tensorflow | closed | Bug: instantiating dynamic_rnn with tf.int32 in input and state raises TypeError | type:bug/performance | **System information**
- OS Platform: OS X 10.13.3
- Custom code
- tensorflow version: 1.12.0
- python version: 3.6.5
**Describe the current behavior**
Tensorflow raises a TypeError when creating a dynamic_rnn with tf.int32 type in its input and state. When changing the type to tf.float32 the error is not raised.
**Describe the expected behavior**
Ideally, a dynamic_rnn should support tf.in32 types. If there's any reason why instantiating a dynamic_rnn with tf.int32 type in its input and state should not be allowed, a custom error should be raised.
**Code to reproduce the issue**
The code below reproduces the error:
```
import tensorflow as tf
X = tf.placeholder(tf.int32, [None, 10, 1])
cell = tf.nn.rnn_cell.LSTMCell(1, dtype=tf.int32)
output, state = tf.nn.dynamic_rnn(cell=cell, inputs=X, dtype=tf.int32)
```
The code below doesn't:
```
import tensorflow as tf
X = tf.placeholder(tf.float32, [None, 10, 1])
cell = tf.nn.rnn_cell.LSTMCell(1, dtype=tf.float32)
output, state = tf.nn.dynamic_rnn(cell=cell, inputs=X, dtype=tf.float32)
```
Note the change in dtype.
**Other info / logs**
TRACEBACK:
---------------------------------------------------------------------------
TypeError Traceback (most recent call last)
<ipython-input-3-1d83a30f7748> in <module>()
2 X = tf.placeholder(tf.int32, [None, 10, 1])
3 cell = tf.nn.rnn_cell.LSTMCell(1, dtype=tf.int32)
----> 4 output, state = tf.nn.dynamic_rnn(cell=cell, inputs=X, dtype=tf.int32)#, initial_state=state)
5
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/ops/rnn.py in dynamic_rnn(cell, inputs, sequence_length, initial_state, dtype, parallel_iterations, swap_memory, time_major, scope)
662 swap_memory=swap_memory,
663 sequence_length=sequence_length,
--> 664 dtype=dtype)
665
666 # Outputs of _dynamic_rnn_loop are always shaped [time, batch, depth].
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/ops/rnn.py in _dynamic_rnn_loop(cell, inputs, initial_state, parallel_iterations, swap_memory, sequence_length, dtype)
870 parallel_iterations=parallel_iterations,
871 maximum_iterations=time_steps,
--> 872 swap_memory=swap_memory)
873
874 # Unpack final output if not using output tuples.
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/ops/control_flow_ops.py in while_loop(cond, body, loop_vars, shape_invariants, parallel_iterations, back_prop, swap_memory, name, maximum_iterations, return_same_structure)
3289 ops.add_to_collection(ops.GraphKeys.WHILE_CONTEXT, loop_context)
3290 result = loop_context.BuildLoop(cond, body, loop_vars, shape_invariants,
-> 3291 return_same_structure)
3292 if maximum_iterations is not None:
3293 return result[1]
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/ops/control_flow_ops.py in BuildLoop(self, pred, body, loop_vars, shape_invariants, return_same_structure)
3002 with ops.get_default_graph()._mutation_lock(): # pylint: disable=protected-access
3003 original_body_result, exit_vars = self._BuildLoop(
-> 3004 pred, body, original_loop_vars, loop_vars, shape_invariants)
3005 finally:
3006 self.Exit()
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/ops/control_flow_ops.py in _BuildLoop(self, pred, body, original_loop_vars, loop_vars, shape_invariants)
2937 flat_sequence=vars_for_body_with_tensor_arrays)
2938 pre_summaries = ops.get_collection(ops.GraphKeys._SUMMARY_COLLECTION) # pylint: disable=protected-access
-> 2939 body_result = body(*packed_vars_for_body)
2940 post_summaries = ops.get_collection(ops.GraphKeys._SUMMARY_COLLECTION) # pylint: disable=protected-access
2941 if not nest.is_sequence(body_result):
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/ops/control_flow_ops.py in <lambda>(i, lv)
3258 cond = lambda i, lv: ( # pylint: disable=g-long-lambda
3259 math_ops.logical_and(i < maximum_iterations, orig_cond(*lv)))
-> 3260 body = lambda i, lv: (i + 1, orig_body(*lv))
3261
3262 if context.executing_eagerly():
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/ops/rnn.py in _time_step(time, output_ta_t, state)
838 skip_conditionals=True)
839 else:
--> 840 (output, new_state) = call_cell()
841
842 # Keras cells always wrap state as list, even if it's a single tensor.
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/ops/rnn.py in <lambda>()
824 if is_keras_rnn_cell and not nest.is_sequence(state):
825 state = [state]
--> 826 call_cell = lambda: cell(input_t, state)
827
828 if sequence_length is not None:
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/ops/rnn_cell_impl.py in __call__(self, inputs, state, scope, *args, **kwargs)
368 # method. See the class docstring for more details.
369 return base_layer.Layer.__call__(self, inputs, state, scope=scope,
--> 370 *args, **kwargs)
371
372
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/layers/base.py in __call__(self, inputs, *args, **kwargs)
372
373 # Actually call layer
--> 374 outputs = super(Layer, self).__call__(inputs, *args, **kwargs)
375
376 if not context.executing_eagerly():
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/keras/engine/base_layer.py in __call__(self, inputs, *args, **kwargs)
755 if not in_deferred_mode:
756 self._in_call = True
--> 757 outputs = self.call(inputs, *args, **kwargs)
758 self._in_call = False
759 if outputs is None:
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/ops/rnn_cell_impl.py in call(self, inputs, state)
1003 sigmoid(i + self._w_i_diag * c_prev) * self._activation(j))
1004 else:
-> 1005 c = (sigmoid(f + self._forget_bias) * c_prev + sigmoid(i) *
1006 self._activation(j))
1007
TypeError: unsupported operand type(s) for +: 'Tensor' and 'float' | True | Bug: instantiating dynamic_rnn with tf.int32 in input and state raises TypeError - **System information**
- OS Platform: OS X 10.13.3
- Custom code
- tensorflow version: 1.12.0
- python version: 3.6.5
**Describe the current behavior**
Tensorflow raises a TypeError when creating a dynamic_rnn with tf.int32 type in its input and state. When changing the type to tf.float32 the error is not raised.
**Describe the expected behavior**
Ideally, a dynamic_rnn should support tf.in32 types. If there's any reason why instantiating a dynamic_rnn with tf.int32 type in its input and state should not be allowed, a custom error should be raised.
**Code to reproduce the issue**
The code below reproduces the error:
```
import tensorflow as tf
X = tf.placeholder(tf.int32, [None, 10, 1])
cell = tf.nn.rnn_cell.LSTMCell(1, dtype=tf.int32)
output, state = tf.nn.dynamic_rnn(cell=cell, inputs=X, dtype=tf.int32)
```
The code below doesn't:
```
import tensorflow as tf
X = tf.placeholder(tf.float32, [None, 10, 1])
cell = tf.nn.rnn_cell.LSTMCell(1, dtype=tf.float32)
output, state = tf.nn.dynamic_rnn(cell=cell, inputs=X, dtype=tf.float32)
```
Note the change in dtype.
**Other info / logs**
TRACEBACK:
---------------------------------------------------------------------------
TypeError Traceback (most recent call last)
<ipython-input-3-1d83a30f7748> in <module>()
2 X = tf.placeholder(tf.int32, [None, 10, 1])
3 cell = tf.nn.rnn_cell.LSTMCell(1, dtype=tf.int32)
----> 4 output, state = tf.nn.dynamic_rnn(cell=cell, inputs=X, dtype=tf.int32)#, initial_state=state)
5
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/ops/rnn.py in dynamic_rnn(cell, inputs, sequence_length, initial_state, dtype, parallel_iterations, swap_memory, time_major, scope)
662 swap_memory=swap_memory,
663 sequence_length=sequence_length,
--> 664 dtype=dtype)
665
666 # Outputs of _dynamic_rnn_loop are always shaped [time, batch, depth].
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/ops/rnn.py in _dynamic_rnn_loop(cell, inputs, initial_state, parallel_iterations, swap_memory, sequence_length, dtype)
870 parallel_iterations=parallel_iterations,
871 maximum_iterations=time_steps,
--> 872 swap_memory=swap_memory)
873
874 # Unpack final output if not using output tuples.
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/ops/control_flow_ops.py in while_loop(cond, body, loop_vars, shape_invariants, parallel_iterations, back_prop, swap_memory, name, maximum_iterations, return_same_structure)
3289 ops.add_to_collection(ops.GraphKeys.WHILE_CONTEXT, loop_context)
3290 result = loop_context.BuildLoop(cond, body, loop_vars, shape_invariants,
-> 3291 return_same_structure)
3292 if maximum_iterations is not None:
3293 return result[1]
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/ops/control_flow_ops.py in BuildLoop(self, pred, body, loop_vars, shape_invariants, return_same_structure)
3002 with ops.get_default_graph()._mutation_lock(): # pylint: disable=protected-access
3003 original_body_result, exit_vars = self._BuildLoop(
-> 3004 pred, body, original_loop_vars, loop_vars, shape_invariants)
3005 finally:
3006 self.Exit()
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/ops/control_flow_ops.py in _BuildLoop(self, pred, body, original_loop_vars, loop_vars, shape_invariants)
2937 flat_sequence=vars_for_body_with_tensor_arrays)
2938 pre_summaries = ops.get_collection(ops.GraphKeys._SUMMARY_COLLECTION) # pylint: disable=protected-access
-> 2939 body_result = body(*packed_vars_for_body)
2940 post_summaries = ops.get_collection(ops.GraphKeys._SUMMARY_COLLECTION) # pylint: disable=protected-access
2941 if not nest.is_sequence(body_result):
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/ops/control_flow_ops.py in <lambda>(i, lv)
3258 cond = lambda i, lv: ( # pylint: disable=g-long-lambda
3259 math_ops.logical_and(i < maximum_iterations, orig_cond(*lv)))
-> 3260 body = lambda i, lv: (i + 1, orig_body(*lv))
3261
3262 if context.executing_eagerly():
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/ops/rnn.py in _time_step(time, output_ta_t, state)
838 skip_conditionals=True)
839 else:
--> 840 (output, new_state) = call_cell()
841
842 # Keras cells always wrap state as list, even if it's a single tensor.
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/ops/rnn.py in <lambda>()
824 if is_keras_rnn_cell and not nest.is_sequence(state):
825 state = [state]
--> 826 call_cell = lambda: cell(input_t, state)
827
828 if sequence_length is not None:
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/ops/rnn_cell_impl.py in __call__(self, inputs, state, scope, *args, **kwargs)
368 # method. See the class docstring for more details.
369 return base_layer.Layer.__call__(self, inputs, state, scope=scope,
--> 370 *args, **kwargs)
371
372
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/layers/base.py in __call__(self, inputs, *args, **kwargs)
372
373 # Actually call layer
--> 374 outputs = super(Layer, self).__call__(inputs, *args, **kwargs)
375
376 if not context.executing_eagerly():
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/keras/engine/base_layer.py in __call__(self, inputs, *args, **kwargs)
755 if not in_deferred_mode:
756 self._in_call = True
--> 757 outputs = self.call(inputs, *args, **kwargs)
758 self._in_call = False
759 if outputs is None:
~/jonassucks3/lib/python3.6/site-packages/tensorflow/python/ops/rnn_cell_impl.py in call(self, inputs, state)
1003 sigmoid(i + self._w_i_diag * c_prev) * self._activation(j))
1004 else:
-> 1005 c = (sigmoid(f + self._forget_bias) * c_prev + sigmoid(i) *
1006 self._activation(j))
1007
TypeError: unsupported operand type(s) for +: 'Tensor' and 'float' | non_design | bug instantiating dynamic rnn with tf in input and state raises typeerror system information os platform os x custom code tensorflow version python version describe the current behavior tensorflow raises a typeerror when creating a dynamic rnn with tf type in its input and state when changing the type to tf the error is not raised describe the expected behavior ideally a dynamic rnn should support tf types if there s any reason why instantiating a dynamic rnn with tf type in its input and state should not be allowed a custom error should be raised code to reproduce the issue the code below reproduces the error import tensorflow as tf x tf placeholder tf cell tf nn rnn cell lstmcell dtype tf output state tf nn dynamic rnn cell cell inputs x dtype tf the code below doesn t import tensorflow as tf x tf placeholder tf cell tf nn rnn cell lstmcell dtype tf output state tf nn dynamic rnn cell cell inputs x dtype tf note the change in dtype other info logs traceback typeerror traceback most recent call last in x tf placeholder tf cell tf nn rnn cell lstmcell dtype tf output state tf nn dynamic rnn cell cell inputs x dtype tf initial state state lib site packages tensorflow python ops rnn py in dynamic rnn cell inputs sequence length initial state dtype parallel iterations swap memory time major scope swap memory swap memory sequence length sequence length dtype dtype outputs of dynamic rnn loop are always shaped lib site packages tensorflow python ops rnn py in dynamic rnn loop cell inputs initial state parallel iterations swap memory sequence length dtype parallel iterations parallel iterations maximum iterations time steps swap memory swap memory unpack final output if not using output tuples lib site packages tensorflow python ops control flow ops py in while loop cond body loop vars shape invariants parallel iterations back prop swap memory name maximum iterations return same structure ops add to collection ops graphkeys while context loop context result loop context buildloop cond body loop vars shape invariants return same structure if maximum iterations is not none return result lib site packages tensorflow python ops control flow ops py in buildloop self pred body loop vars shape invariants return same structure with ops get default graph mutation lock pylint disable protected access original body result exit vars self buildloop pred body original loop vars loop vars shape invariants finally self exit lib site packages tensorflow python ops control flow ops py in buildloop self pred body original loop vars loop vars shape invariants flat sequence vars for body with tensor arrays pre summaries ops get collection ops graphkeys summary collection pylint disable protected access body result body packed vars for body post summaries ops get collection ops graphkeys summary collection pylint disable protected access if not nest is sequence body result lib site packages tensorflow python ops control flow ops py in i lv cond lambda i lv pylint disable g long lambda math ops logical and i maximum iterations orig cond lv body lambda i lv i orig body lv if context executing eagerly lib site packages tensorflow python ops rnn py in time step time output ta t state skip conditionals true else output new state call cell keras cells always wrap state as list even if it s a single tensor lib site packages tensorflow python ops rnn py in if is keras rnn cell and not nest is sequence state state call cell lambda cell input t state if sequence length is not none lib site packages tensorflow python ops rnn cell impl py in call self inputs state scope args kwargs method see the class docstring for more details return base layer layer call self inputs state scope scope args kwargs lib site packages tensorflow python layers base py in call self inputs args kwargs actually call layer outputs super layer self call inputs args kwargs if not context executing eagerly lib site packages tensorflow python keras engine base layer py in call self inputs args kwargs if not in deferred mode self in call true outputs self call inputs args kwargs self in call false if outputs is none lib site packages tensorflow python ops rnn cell impl py in call self inputs state sigmoid i self w i diag c prev self activation j else c sigmoid f self forget bias c prev sigmoid i self activation j typeerror unsupported operand type s for tensor and float | 0 |
27,882 | 13,448,525,372 | IssuesEvent | 2020-09-08 15:35:00 | Stillat/meerkat-statamic3 | https://api.github.com/repos/Stillat/meerkat-statamic3 | opened | Antlers Tags: Automatic Markdown | antlers performance | Provide a parameter `markdown="true/false"` to enable or disable automatic markdown conversion when displaying threads in templates.
Default should be `false` and encourage users to utilize existing Antlers modifiers. | True | Antlers Tags: Automatic Markdown - Provide a parameter `markdown="true/false"` to enable or disable automatic markdown conversion when displaying threads in templates.
Default should be `false` and encourage users to utilize existing Antlers modifiers. | non_design | antlers tags automatic markdown provide a parameter markdown true false to enable or disable automatic markdown conversion when displaying threads in templates default should be false and encourage users to utilize existing antlers modifiers | 0 |
141,808 | 21,626,040,454 | IssuesEvent | 2022-05-05 02:23:06 | JordanMartinez/purescript-jordans-reference | https://api.github.com/repos/JordanMartinez/purescript-jordans-reference | closed | Incorporating "Free X" data structures into custom ADTs | Design-Patterns | Given some ADT for one's particular usage where some parts could be monoidic but other parts aren't..
```purs
data Foo a b
= Bar a Foo b
| Baz Foo a a
appendIsh :: forall a b. Foo a b -> Foo a b -> Foo a b
appendIsh = case _, _ of
Baz foo a1 a2, Baz foo2 a3 a4 ->
Baz (foo1 <> foo2) (a1 <> a3) (a2 <> a4)
_, _ -> -- uh......
```
a `Monoid` instance can still be created if one incorporates an encoding of the Free Monoid (e.g. `List`) into the data structure itself:
```purs
data Foo a b
= Bar a Foo b
| Baz Foo a a
| Append (Foo a b) (Foo a b) -- Tree-like `Cons`
| Empty -- `Nil`
instance Semigroup (Foo a b) where
append = case _, _ of
Baz foo a1 a2, Baz foo2 a3 a4 ->
Baz (foo1 <> foo2) (a1 <> a3) (a2 <> a4)
l, r -> Append l r
instance Monoid (Foo a b) where
mempty = Empty
```
This idea works for `Semigroup` and `Monoid`. Incorporating other such parts from Free data structures into custom ADTs may also apply. I'm not sure whether this pattern has a name, nor what to call it if it doesn't have one. | 1.0 | Incorporating "Free X" data structures into custom ADTs - Given some ADT for one's particular usage where some parts could be monoidic but other parts aren't..
```purs
data Foo a b
= Bar a Foo b
| Baz Foo a a
appendIsh :: forall a b. Foo a b -> Foo a b -> Foo a b
appendIsh = case _, _ of
Baz foo a1 a2, Baz foo2 a3 a4 ->
Baz (foo1 <> foo2) (a1 <> a3) (a2 <> a4)
_, _ -> -- uh......
```
a `Monoid` instance can still be created if one incorporates an encoding of the Free Monoid (e.g. `List`) into the data structure itself:
```purs
data Foo a b
= Bar a Foo b
| Baz Foo a a
| Append (Foo a b) (Foo a b) -- Tree-like `Cons`
| Empty -- `Nil`
instance Semigroup (Foo a b) where
append = case _, _ of
Baz foo a1 a2, Baz foo2 a3 a4 ->
Baz (foo1 <> foo2) (a1 <> a3) (a2 <> a4)
l, r -> Append l r
instance Monoid (Foo a b) where
mempty = Empty
```
This idea works for `Semigroup` and `Monoid`. Incorporating other such parts from Free data structures into custom ADTs may also apply. I'm not sure whether this pattern has a name, nor what to call it if it doesn't have one. | design | incorporating free x data structures into custom adts given some adt for one s particular usage where some parts could be monoidic but other parts aren t purs data foo a b bar a foo b baz foo a a appendish forall a b foo a b foo a b foo a b appendish case of baz foo baz baz uh a monoid instance can still be created if one incorporates an encoding of the free monoid e g list into the data structure itself purs data foo a b bar a foo b baz foo a a append foo a b foo a b tree like cons empty nil instance semigroup foo a b where append case of baz foo baz baz l r append l r instance monoid foo a b where mempty empty this idea works for semigroup and monoid incorporating other such parts from free data structures into custom adts may also apply i m not sure whether this pattern has a name nor what to call it if it doesn t have one | 1 |
59,969 | 14,681,665,824 | IssuesEvent | 2020-12-31 13:59:08 | appsmithorg/appsmith | https://api.github.com/repos/appsmithorg/appsmith | opened | [Feature] Allow users to control visibility for role groups | Property Pane UI Building advanced | ## Summary
1. Let users control what roles can see a widget or a page
2. Let users discover how to write visibility logic in JS inside Appsmith for different user groups(you’ll see the JS snippet when you click JS toggle)
This will help a developer see widgets+pages in deployed version that are invisible to a business user.
1. Make visibility a dropdown instead of a toggle(example below)
2. The view mode pages shouldn’t slow down because at every page load we have to check visibility permissions for a user.
2. It should be easy to change visibility controls for a group of users from a single location when you deploy instead of having to visit 10 different places to make a change.
<img width="571" alt="Screen Shot 2020-12-30 at 2 48 20 PM" src="https://user-images.githubusercontent.com/30255708/103413168-60730a00-4b9e-11eb-8634-fed3a99f4d67.png">
| 1.0 | [Feature] Allow users to control visibility for role groups - ## Summary
1. Let users control what roles can see a widget or a page
2. Let users discover how to write visibility logic in JS inside Appsmith for different user groups(you’ll see the JS snippet when you click JS toggle)
This will help a developer see widgets+pages in deployed version that are invisible to a business user.
1. Make visibility a dropdown instead of a toggle(example below)
2. The view mode pages shouldn’t slow down because at every page load we have to check visibility permissions for a user.
2. It should be easy to change visibility controls for a group of users from a single location when you deploy instead of having to visit 10 different places to make a change.
<img width="571" alt="Screen Shot 2020-12-30 at 2 48 20 PM" src="https://user-images.githubusercontent.com/30255708/103413168-60730a00-4b9e-11eb-8634-fed3a99f4d67.png">
| non_design | allow users to control visibility for role groups summary let users control what roles can see a widget or a page let users discover how to write visibility logic in js inside appsmith for different user groups you’ll see the js snippet when you click js toggle this will help a developer see widgets pages in deployed version that are invisible to a business user make visibility a dropdown instead of a toggle example below the view mode pages shouldn’t slow down because at every page load we have to check visibility permissions for a user it should be easy to change visibility controls for a group of users from a single location when you deploy instead of having to visit different places to make a change img width alt screen shot at pm src | 0 |
661,016 | 22,038,573,404 | IssuesEvent | 2022-05-29 01:23:15 | googleapis/google-cloud-cpp | https://api.github.com/repos/googleapis/google-cloud-cpp | closed | GCS+gRPC crashes when enabling progress-based timeouts in ReadObject() | type: bug api: storage priority: p2 | This affects the GCS+gRPC plugin, and only if the progress-based timeouts (see #7300) are enabled. On a normal build the crash generates a "pure virtual called" message. With an msan build we get more information (see below).
```
==19==WARNING: MemorySanitizer: use-of-uninitialized-value
CppClient,Grpc,WRITE,2022-05-27T21:40:24.676898Z,140268505,140268505,26476544,8388608,1,0,26813581,7365968,unknown,OK,
CppClient,Grpc,WRITE,2022-05-27T21:40:22.940905Z,131429351,131429351,61079552,8388608,1,0,28444396,7764406,unknown,OK,
#0 0xfb7b93 in grpc::internal::MetadataMap::GetBinaryErrorDetails() /proc/self/cwd/external/com_github_grpc_grpc/include/grpcpp/impl/codegen/metadata_map.h:43:9
#1 0xfb3fdc in grpc::internal::CallOpClientRecvStatus::FinishOp(bool*) /proc/self/cwd/external/com_github_grpc_grpc/include/grpcpp/impl/codegen/call_op_set.h:813:33
#2 0x10a804b in grpc::internal::CallOpSet<grpc::internal::CallOpRecvInitialMetadata, grpc::internal::CallOpClientRecvStatus, grpc::internal::CallNoOp<3>, grpc::internal::CallNoOp<4>, grpc::internal::CallNoOp<5>, grpc::internal::CallNoOp<6> >::FinalizeResult(void**, bool*) /proc/self/cwd/external/com_github_grpc_grpc/include/grpcpp/impl/codegen/call_op_set.h:927:16
#3 0x17e15ba in grpc::CompletionQueue::AsyncNextInternal(void**, bool*, gpr_timespec) /proc/self/cwd/external/com_github_grpc_grpc/src/cpp/common/completion_queue_cc.cc:157:26
#4 0xf6a0dc in grpc::CompletionQueue::NextStatus grpc::CompletionQueue::AsyncNext<std::__1::chrono::time_point<std::__1::chrono::system_clock, std::__1::chrono::duration<long long, std::__1::ratio<1l, 1000000l> > > >(void**, bool*, std::__1::chrono::time_point<std::__1::chrono::system_clock, std::__1::chrono::duration<long long, std::__1::ratio<1l, 1000000l> > > const&) /proc/self/cwd/external/com_github_grpc_grpc/include/grpcpp/impl/codegen/completion_queue.h:204:12
#5 0xf6a0dc in google::cloud::v1_41_0::internal::DefaultCompletionQueueImpl::Run() /proc/self/cwd/google/cloud/internal/default_completion_queue_impl.cc:179:21
#6 0xf34959 in google::cloud::v1_41_0::CompletionQueue::Run() /proc/self/cwd/./google/cloud/completion_queue.h:53:23
#7 0xf34959 in google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&)::operator()(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&) const /proc/self/cwd/google/cloud/internal/background_threads_impl.cc:34:14
#8 0xf34959 in decltype(std::__1::forward<google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&)>(fp)(std::__1::forward<google::cloud::v1_41_0::CompletionQueue>(fp0), std::__1::forward<std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> > >(fp0))) std::__1::__invoke<google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&), google::cloud::v1_41_0::CompletionQueue, std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> > >(google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&)&&, google::cloud::v1_41_0::CompletionQueue&&, std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> >&&) /usr/bin/../include/c++/v1/type_traits:3899:1
#9 0xf34959 in void std::__1::__thread_execute<std::__1::unique_ptr<std::__1::__thread_struct, std::__1::default_delete<std::__1::__thread_struct> >, google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&), google::cloud::v1_41_0::CompletionQueue, std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> >, 2ul, 3ul>(std::__1::tuple<std::__1::unique_ptr<std::__1::__thread_struct, std::__1::default_delete<std::__1::__thread_struct> >, google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&), google::cloud::v1_41_0::CompletionQueue, std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> > >&, std::__1::__tuple_indices<2ul, 3ul>) /usr/bin/../include/c++/v1/thread:280:5
#10 0xf34959 in void* std::__1::__thread_proxy<std::__1::tuple<std::__1::unique_ptr<std::__1::__thread_struct, std::__1::default_delete<std::__1::__thread_struct> >, google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&), google::cloud::v1_41_0::CompletionQueue, std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> > > >(void*) /usr/bin/../include/c++/v1/thread:291:5
#11 0x7f15a5055b16 in start_thread (/lib64/libc.so.6+0x8db16)
#12 0x7f15a50d9933 in __clone (/lib64/libc.so.6+0x111933)
Uninitialized value was created by a heap deallocation
#0 0x7d61f2 in __interceptor_free (/h/.cache/bazel/_bazel_coryan/eab0d61a99b6696edb3d2aff87b585e8/execroot/com_github_googleapis_google_cloud_cpp/bazel-out/k8-fastbuild/bin/google/cloud/storage/benchmarks/storage_throughput_vs_cpu_benchmark+0x7d61f2)
#1 0xa2d188 in std::__1::default_delete<grpc::ClientContext>::operator()(grpc::ClientContext*) const /usr/bin/../include/c++/v1/memory:2262:5
#2 0xa2d188 in std::__1::unique_ptr<grpc::ClientContext, std::__1::default_delete<grpc::ClientContext> >::reset(grpc::ClientContext*) /usr/bin/../include/c++/v1/memory:2517:7
#3 0xa2d188 in std::__1::unique_ptr<grpc::ClientContext, std::__1::default_delete<grpc::ClientContext> >::~unique_ptr() /usr/bin/../include/c++/v1/memory:2471:19
#4 0xa2d188 in google::cloud::v1_41_0::internal::AsyncStreamingReadRpcImpl<google::storage::v2::ReadObjectResponse>::~AsyncStreamingReadRpcImpl() /proc/self/cwd/./google/cloud/internal/async_streaming_read_rpc_impl.h:42:7
#5 0xa2d2fc in google::cloud::v1_41_0::internal::AsyncStreamingReadRpcImpl<google::storage::v2::ReadObjectResponse>::~AsyncStreamingReadRpcImpl() /proc/self/cwd/./google/cloud/internal/async_streaming_read_rpc_impl.h:42:7
#6 0x955977 in std::__1::default_delete<google::cloud::v1_41_0::internal::AsyncStreamingReadRpc<google::storage::v2::ReadObjectResponse> >::operator()(google::cloud::v1_41_0::internal::AsyncStreamingReadRpc<google::storage::v2::ReadObjectResponse>*) const /usr/bin/../include/c++/v1/memory:2262:5
#7 0x955977 in std::__1::unique_ptr<google::cloud::v1_41_0::internal::AsyncStreamingReadRpc<google::storage::v2::ReadObjectResponse>, std::__1::default_delete<google::cloud::v1_41_0::internal::AsyncStreamingReadRpc<google::storage::v2::ReadObjectResponse> > >::reset(google::cloud::v1_41_0::internal::AsyncStreamingReadRpc<google::storage::v2::ReadObjectResponse>*) /usr/bin/../include/c++/v1/memory:2517:7
#8 0x955977 in google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove::operator()(google::cloud::v1_41_0::future<absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse> >) /proc/self/cwd/google/cloud/storage/internal/grpc_object_read_source.cc:123:18
#9 0x955977 in google::cloud::v1_41_0::internal::then_helper<google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove, absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse>, 0>::future_t google::cloud::v1_41_0::future<absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse> >::then_impl<google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove>(google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove&&, std::__1::integral_constant<bool, false>)::adapter::operator()(std::__1::shared_ptr<google::cloud::v1_41_0::internal::future_shared_state<absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse> > >) /proc/self/cwd/./google/cloud/internal/future_then_impl.h:71:14
#10 0x955977 in void google::cloud::v1_41_0::internal::continuation_execute_delegate<google::cloud::v1_41_0::internal::then_helper<google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove, absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse>, 0>::future_t google::cloud::v1_41_0::future<absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse> >::then_impl<google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove>(google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove&&, std::__1::integral_constant<bool, false>)::adapter, absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse> >(google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove&, std::__1::shared_ptr<google::cloud::v1_41_0::internal::future_shared_state<absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse> > >, google::cloud::v1_41_0::internal::future_shared_state<void>&, std::__1::integral_constant<bool, false>) /proc/self/cwd/./google/cloud/internal/future_impl.h:614:5
#11 0x955977 in google::cloud::v1_41_0::internal::continuation<google::cloud::v1_41_0::internal::then_helper<google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove, absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse>, 0>::future_t google::cloud::v1_41_0::future<absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse> >::then_impl<google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove>(google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove&&, std::__1::integral_constant<bool, false>)::adapter, absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse> >::execute() /proc/self/cwd/./google/cloud/internal/future_impl.h:672:5
#12 0x9cc86e in google::cloud::v1_41_0::internal::future_shared_state_base::notify_now(std::__1::unique_lock<std::__1::mutex>) /proc/self/cwd/./google/cloud/internal/future_impl.h:242:22
#13 0x9cc86e in google::cloud::v1_41_0::internal::future_shared_state<absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse> >::set_value(absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse>) /proc/self/cwd/./google/cloud/internal/future_impl.h:393:5
#14 0x9ca76a in google::cloud::v1_41_0::promise<absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse> >::set_value(absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse>) /proc/self/cwd/./google/cloud/future_generic.h:209:26
#15 0xa30374 in google::cloud::v1_41_0::internal::AsyncStreamingReadRpcImpl<google::storage::v2::ReadObjectResponse>::Read()::OnRead::Notify(bool) /proc/self/cwd/./google/cloud/internal/async_streaming_read_rpc_impl.h:81:11
#16 0xf69e99 in google::cloud::v1_41_0::internal::DefaultCompletionQueueImpl::Run() /proc/self/cwd/google/cloud/internal/default_completion_queue_impl.cc:187:13
#17 0xf34959 in google::cloud::v1_41_0::CompletionQueue::Run() /proc/self/cwd/./google/cloud/completion_queue.h:53:23
#18 0xf34959 in google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&)::operator()(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&) const /proc/self/cwd/google/cloud/internal/background_threads_impl.cc:34:14
#19 0xf34959 in decltype(std::__1::forward<google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&)>(fp)(std::__1::forward<google::cloud::v1_41_0::CompletionQueue>(fp0), std::__1::forward<std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> > >(fp0))) std::__1::__invoke<google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&), google::cloud::v1_41_0::CompletionQueue, std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> > >(google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&)&&, google::cloud::v1_41_0::CompletionQueue&&, std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> >&&) /usr/bin/../include/c++/v1/type_traits:3899:1
#20 0xf34959 in void std::__1::__thread_execute<std::__1::unique_ptr<std::__1::__thread_struct, std::__1::default_delete<std::__1::__thread_struct> >, google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&), google::cloud::v1_41_0::CompletionQueue, std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> >, 2ul, 3ul>(std::__1::tuple<std::__1::unique_ptr<std::__1::__thread_struct, std::__1::default_delete<std::__1::__thread_struct> >, google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&), google::cloud::v1_41_0::CompletionQueue, std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> > >&, std::__1::__tuple_indices<2ul, 3ul>) /usr/bin/../include/c++/v1/thread:280:5
#21 0xf34959 in void* std::__1::__thread_proxy<std::__1::tuple<std::__1::unique_ptr<std::__1::__thread_struct, std::__1::default_delete<std::__1::__thread_struct> >, google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&), google::cloud::v1_41_0::CompletionQueue, std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> > > >(void*) /usr/bin/../include/c++/v1/thread:291:5
#22 0x7f15a5055b16 in start_thread (/lib64/libc.so.6+0x8db16)
SUMMARY: MemorySanitizer: use-of-uninitialized-value /proc/self/cwd/external/com_github_grpc_grpc/include/grpcpp/impl/codegen/metadata_map.h:43:9 in grpc::internal::MetadataMap::GetBinaryErrorDetails()
Exiting
```
| 1.0 | GCS+gRPC crashes when enabling progress-based timeouts in ReadObject() - This affects the GCS+gRPC plugin, and only if the progress-based timeouts (see #7300) are enabled. On a normal build the crash generates a "pure virtual called" message. With an msan build we get more information (see below).
```
==19==WARNING: MemorySanitizer: use-of-uninitialized-value
CppClient,Grpc,WRITE,2022-05-27T21:40:24.676898Z,140268505,140268505,26476544,8388608,1,0,26813581,7365968,unknown,OK,
CppClient,Grpc,WRITE,2022-05-27T21:40:22.940905Z,131429351,131429351,61079552,8388608,1,0,28444396,7764406,unknown,OK,
#0 0xfb7b93 in grpc::internal::MetadataMap::GetBinaryErrorDetails() /proc/self/cwd/external/com_github_grpc_grpc/include/grpcpp/impl/codegen/metadata_map.h:43:9
#1 0xfb3fdc in grpc::internal::CallOpClientRecvStatus::FinishOp(bool*) /proc/self/cwd/external/com_github_grpc_grpc/include/grpcpp/impl/codegen/call_op_set.h:813:33
#2 0x10a804b in grpc::internal::CallOpSet<grpc::internal::CallOpRecvInitialMetadata, grpc::internal::CallOpClientRecvStatus, grpc::internal::CallNoOp<3>, grpc::internal::CallNoOp<4>, grpc::internal::CallNoOp<5>, grpc::internal::CallNoOp<6> >::FinalizeResult(void**, bool*) /proc/self/cwd/external/com_github_grpc_grpc/include/grpcpp/impl/codegen/call_op_set.h:927:16
#3 0x17e15ba in grpc::CompletionQueue::AsyncNextInternal(void**, bool*, gpr_timespec) /proc/self/cwd/external/com_github_grpc_grpc/src/cpp/common/completion_queue_cc.cc:157:26
#4 0xf6a0dc in grpc::CompletionQueue::NextStatus grpc::CompletionQueue::AsyncNext<std::__1::chrono::time_point<std::__1::chrono::system_clock, std::__1::chrono::duration<long long, std::__1::ratio<1l, 1000000l> > > >(void**, bool*, std::__1::chrono::time_point<std::__1::chrono::system_clock, std::__1::chrono::duration<long long, std::__1::ratio<1l, 1000000l> > > const&) /proc/self/cwd/external/com_github_grpc_grpc/include/grpcpp/impl/codegen/completion_queue.h:204:12
#5 0xf6a0dc in google::cloud::v1_41_0::internal::DefaultCompletionQueueImpl::Run() /proc/self/cwd/google/cloud/internal/default_completion_queue_impl.cc:179:21
#6 0xf34959 in google::cloud::v1_41_0::CompletionQueue::Run() /proc/self/cwd/./google/cloud/completion_queue.h:53:23
#7 0xf34959 in google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&)::operator()(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&) const /proc/self/cwd/google/cloud/internal/background_threads_impl.cc:34:14
#8 0xf34959 in decltype(std::__1::forward<google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&)>(fp)(std::__1::forward<google::cloud::v1_41_0::CompletionQueue>(fp0), std::__1::forward<std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> > >(fp0))) std::__1::__invoke<google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&), google::cloud::v1_41_0::CompletionQueue, std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> > >(google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&)&&, google::cloud::v1_41_0::CompletionQueue&&, std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> >&&) /usr/bin/../include/c++/v1/type_traits:3899:1
#9 0xf34959 in void std::__1::__thread_execute<std::__1::unique_ptr<std::__1::__thread_struct, std::__1::default_delete<std::__1::__thread_struct> >, google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&), google::cloud::v1_41_0::CompletionQueue, std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> >, 2ul, 3ul>(std::__1::tuple<std::__1::unique_ptr<std::__1::__thread_struct, std::__1::default_delete<std::__1::__thread_struct> >, google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&), google::cloud::v1_41_0::CompletionQueue, std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> > >&, std::__1::__tuple_indices<2ul, 3ul>) /usr/bin/../include/c++/v1/thread:280:5
#10 0xf34959 in void* std::__1::__thread_proxy<std::__1::tuple<std::__1::unique_ptr<std::__1::__thread_struct, std::__1::default_delete<std::__1::__thread_struct> >, google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&), google::cloud::v1_41_0::CompletionQueue, std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> > > >(void*) /usr/bin/../include/c++/v1/thread:291:5
#11 0x7f15a5055b16 in start_thread (/lib64/libc.so.6+0x8db16)
#12 0x7f15a50d9933 in __clone (/lib64/libc.so.6+0x111933)
Uninitialized value was created by a heap deallocation
#0 0x7d61f2 in __interceptor_free (/h/.cache/bazel/_bazel_coryan/eab0d61a99b6696edb3d2aff87b585e8/execroot/com_github_googleapis_google_cloud_cpp/bazel-out/k8-fastbuild/bin/google/cloud/storage/benchmarks/storage_throughput_vs_cpu_benchmark+0x7d61f2)
#1 0xa2d188 in std::__1::default_delete<grpc::ClientContext>::operator()(grpc::ClientContext*) const /usr/bin/../include/c++/v1/memory:2262:5
#2 0xa2d188 in std::__1::unique_ptr<grpc::ClientContext, std::__1::default_delete<grpc::ClientContext> >::reset(grpc::ClientContext*) /usr/bin/../include/c++/v1/memory:2517:7
#3 0xa2d188 in std::__1::unique_ptr<grpc::ClientContext, std::__1::default_delete<grpc::ClientContext> >::~unique_ptr() /usr/bin/../include/c++/v1/memory:2471:19
#4 0xa2d188 in google::cloud::v1_41_0::internal::AsyncStreamingReadRpcImpl<google::storage::v2::ReadObjectResponse>::~AsyncStreamingReadRpcImpl() /proc/self/cwd/./google/cloud/internal/async_streaming_read_rpc_impl.h:42:7
#5 0xa2d2fc in google::cloud::v1_41_0::internal::AsyncStreamingReadRpcImpl<google::storage::v2::ReadObjectResponse>::~AsyncStreamingReadRpcImpl() /proc/self/cwd/./google/cloud/internal/async_streaming_read_rpc_impl.h:42:7
#6 0x955977 in std::__1::default_delete<google::cloud::v1_41_0::internal::AsyncStreamingReadRpc<google::storage::v2::ReadObjectResponse> >::operator()(google::cloud::v1_41_0::internal::AsyncStreamingReadRpc<google::storage::v2::ReadObjectResponse>*) const /usr/bin/../include/c++/v1/memory:2262:5
#7 0x955977 in std::__1::unique_ptr<google::cloud::v1_41_0::internal::AsyncStreamingReadRpc<google::storage::v2::ReadObjectResponse>, std::__1::default_delete<google::cloud::v1_41_0::internal::AsyncStreamingReadRpc<google::storage::v2::ReadObjectResponse> > >::reset(google::cloud::v1_41_0::internal::AsyncStreamingReadRpc<google::storage::v2::ReadObjectResponse>*) /usr/bin/../include/c++/v1/memory:2517:7
#8 0x955977 in google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove::operator()(google::cloud::v1_41_0::future<absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse> >) /proc/self/cwd/google/cloud/storage/internal/grpc_object_read_source.cc:123:18
#9 0x955977 in google::cloud::v1_41_0::internal::then_helper<google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove, absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse>, 0>::future_t google::cloud::v1_41_0::future<absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse> >::then_impl<google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove>(google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove&&, std::__1::integral_constant<bool, false>)::adapter::operator()(std::__1::shared_ptr<google::cloud::v1_41_0::internal::future_shared_state<absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse> > >) /proc/self/cwd/./google/cloud/internal/future_then_impl.h:71:14
#10 0x955977 in void google::cloud::v1_41_0::internal::continuation_execute_delegate<google::cloud::v1_41_0::internal::then_helper<google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove, absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse>, 0>::future_t google::cloud::v1_41_0::future<absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse> >::then_impl<google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove>(google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove&&, std::__1::integral_constant<bool, false>)::adapter, absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse> >(google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove&, std::__1::shared_ptr<google::cloud::v1_41_0::internal::future_shared_state<absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse> > >, google::cloud::v1_41_0::internal::future_shared_state<void>&, std::__1::integral_constant<bool, false>) /proc/self/cwd/./google/cloud/internal/future_impl.h:614:5
#11 0x955977 in google::cloud::v1_41_0::internal::continuation<google::cloud::v1_41_0::internal::then_helper<google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove, absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse>, 0>::future_t google::cloud::v1_41_0::future<absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse> >::then_impl<google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove>(google::cloud::storage::v1_41_0::internal::GrpcObjectReadSource::Read(char*, unsigned long)::CaptureByMove&&, std::__1::integral_constant<bool, false>)::adapter, absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse> >::execute() /proc/self/cwd/./google/cloud/internal/future_impl.h:672:5
#12 0x9cc86e in google::cloud::v1_41_0::internal::future_shared_state_base::notify_now(std::__1::unique_lock<std::__1::mutex>) /proc/self/cwd/./google/cloud/internal/future_impl.h:242:22
#13 0x9cc86e in google::cloud::v1_41_0::internal::future_shared_state<absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse> >::set_value(absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse>) /proc/self/cwd/./google/cloud/internal/future_impl.h:393:5
#14 0x9ca76a in google::cloud::v1_41_0::promise<absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse> >::set_value(absl::lts_20211102::optional<google::storage::v2::ReadObjectResponse>) /proc/self/cwd/./google/cloud/future_generic.h:209:26
#15 0xa30374 in google::cloud::v1_41_0::internal::AsyncStreamingReadRpcImpl<google::storage::v2::ReadObjectResponse>::Read()::OnRead::Notify(bool) /proc/self/cwd/./google/cloud/internal/async_streaming_read_rpc_impl.h:81:11
#16 0xf69e99 in google::cloud::v1_41_0::internal::DefaultCompletionQueueImpl::Run() /proc/self/cwd/google/cloud/internal/default_completion_queue_impl.cc:187:13
#17 0xf34959 in google::cloud::v1_41_0::CompletionQueue::Run() /proc/self/cwd/./google/cloud/completion_queue.h:53:23
#18 0xf34959 in google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&)::operator()(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&) const /proc/self/cwd/google/cloud/internal/background_threads_impl.cc:34:14
#19 0xf34959 in decltype(std::__1::forward<google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&)>(fp)(std::__1::forward<google::cloud::v1_41_0::CompletionQueue>(fp0), std::__1::forward<std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> > >(fp0))) std::__1::__invoke<google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&), google::cloud::v1_41_0::CompletionQueue, std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> > >(google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&)&&, google::cloud::v1_41_0::CompletionQueue&&, std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> >&&) /usr/bin/../include/c++/v1/type_traits:3899:1
#20 0xf34959 in void std::__1::__thread_execute<std::__1::unique_ptr<std::__1::__thread_struct, std::__1::default_delete<std::__1::__thread_struct> >, google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&), google::cloud::v1_41_0::CompletionQueue, std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> >, 2ul, 3ul>(std::__1::tuple<std::__1::unique_ptr<std::__1::__thread_struct, std::__1::default_delete<std::__1::__thread_struct> >, google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&), google::cloud::v1_41_0::CompletionQueue, std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> > >&, std::__1::__tuple_indices<2ul, 3ul>) /usr/bin/../include/c++/v1/thread:280:5
#21 0xf34959 in void* std::__1::__thread_proxy<std::__1::tuple<std::__1::unique_ptr<std::__1::__thread_struct, std::__1::default_delete<std::__1::__thread_struct> >, google::cloud::v1_41_0::internal::AutomaticallyCreatedBackgroundThreads::AutomaticallyCreatedBackgroundThreads(unsigned long)::$_0::operator()() const::'lambda'(google::cloud::v1_41_0::CompletionQueue, google::cloud::v1_41_0::promise<void>&), google::cloud::v1_41_0::CompletionQueue, std::__1::reference_wrapper<google::cloud::v1_41_0::promise<void> > > >(void*) /usr/bin/../include/c++/v1/thread:291:5
#22 0x7f15a5055b16 in start_thread (/lib64/libc.so.6+0x8db16)
SUMMARY: MemorySanitizer: use-of-uninitialized-value /proc/self/cwd/external/com_github_grpc_grpc/include/grpcpp/impl/codegen/metadata_map.h:43:9 in grpc::internal::MetadataMap::GetBinaryErrorDetails()
Exiting
```
| non_design | gcs grpc crashes when enabling progress based timeouts in readobject this affects the gcs grpc plugin and only if the progress based timeouts see are enabled on a normal build the crash generates a pure virtual called message with an msan build we get more information see below warning memorysanitizer use of uninitialized value cppclient grpc write unknown ok cppclient grpc write unknown ok in grpc internal metadatamap getbinaryerrordetails proc self cwd external com github grpc grpc include grpcpp impl codegen metadata map h in grpc internal callopclientrecvstatus finishop bool proc self cwd external com github grpc grpc include grpcpp impl codegen call op set h in grpc internal callopset grpc internal callnoop grpc internal callnoop grpc internal callnoop finalizeresult void bool proc self cwd external com github grpc grpc include grpcpp impl codegen call op set h in grpc completionqueue asyncnextinternal void bool gpr timespec proc self cwd external com github grpc grpc src cpp common completion queue cc cc in grpc completionqueue nextstatus grpc completionqueue asyncnext void bool std chrono time point const proc self cwd external com github grpc grpc include grpcpp impl codegen completion queue h in google cloud internal defaultcompletionqueueimpl run proc self cwd google cloud internal default completion queue impl cc in google cloud completionqueue run proc self cwd google cloud completion queue h in google cloud internal automaticallycreatedbackgroundthreads automaticallycreatedbackgroundthreads unsigned long operator const lambda google cloud completionqueue google cloud promise operator google cloud completionqueue google cloud promise const proc self cwd google cloud internal background threads impl cc in decltype std forward fp std forward std forward std invoke google cloud completionqueue std reference wrapper google cloud internal automaticallycreatedbackgroundthreads automaticallycreatedbackgroundthreads unsigned long operator const lambda google cloud completionqueue google cloud promise google cloud completionqueue std reference wrapper usr bin include c type traits in void std thread execute google cloud internal automaticallycreatedbackgroundthreads automaticallycreatedbackgroundthreads unsigned long operator const lambda google cloud completionqueue google cloud promise google cloud completionqueue std reference wrapper std tuple google cloud internal automaticallycreatedbackgroundthreads automaticallycreatedbackgroundthreads unsigned long operator const lambda google cloud completionqueue google cloud promise google cloud completionqueue std reference wrapper std tuple indices usr bin include c thread in void std thread proxy google cloud internal automaticallycreatedbackgroundthreads automaticallycreatedbackgroundthreads unsigned long operator const lambda google cloud completionqueue google cloud promise google cloud completionqueue std reference wrapper void usr bin include c thread in start thread libc so in clone libc so uninitialized value was created by a heap deallocation in interceptor free h cache bazel bazel coryan execroot com github googleapis google cloud cpp bazel out fastbuild bin google cloud storage benchmarks storage throughput vs cpu benchmark in std default delete operator grpc clientcontext const usr bin include c memory in std unique ptr reset grpc clientcontext usr bin include c memory in std unique ptr unique ptr usr bin include c memory in google cloud internal asyncstreamingreadrpcimpl asyncstreamingreadrpcimpl proc self cwd google cloud internal async streaming read rpc impl h in google cloud internal asyncstreamingreadrpcimpl asyncstreamingreadrpcimpl proc self cwd google cloud internal async streaming read rpc impl h in std default delete operator google cloud internal asyncstreamingreadrpc const usr bin include c memory in std unique ptr std default delete reset google cloud internal asyncstreamingreadrpc usr bin include c memory in google cloud storage internal grpcobjectreadsource read char unsigned long capturebymove operator google cloud future proc self cwd google cloud storage internal grpc object read source cc in google cloud internal then helper future t google cloud future then impl google cloud storage internal grpcobjectreadsource read char unsigned long capturebymove std integral constant adapter operator std shared ptr proc self cwd google cloud internal future then impl h in void google cloud internal continuation execute delegate future t google cloud future then impl google cloud storage internal grpcobjectreadsource read char unsigned long capturebymove std integral constant adapter absl lts optional google cloud storage internal grpcobjectreadsource read char unsigned long capturebymove std shared ptr google cloud internal future shared state std integral constant proc self cwd google cloud internal future impl h in google cloud internal continuation future t google cloud future then impl google cloud storage internal grpcobjectreadsource read char unsigned long capturebymove std integral constant adapter absl lts optional execute proc self cwd google cloud internal future impl h in google cloud internal future shared state base notify now std unique lock proc self cwd google cloud internal future impl h in google cloud internal future shared state set value absl lts optional proc self cwd google cloud internal future impl h in google cloud promise set value absl lts optional proc self cwd google cloud future generic h in google cloud internal asyncstreamingreadrpcimpl read onread notify bool proc self cwd google cloud internal async streaming read rpc impl h in google cloud internal defaultcompletionqueueimpl run proc self cwd google cloud internal default completion queue impl cc in google cloud completionqueue run proc self cwd google cloud completion queue h in google cloud internal automaticallycreatedbackgroundthreads automaticallycreatedbackgroundthreads unsigned long operator const lambda google cloud completionqueue google cloud promise operator google cloud completionqueue google cloud promise const proc self cwd google cloud internal background threads impl cc in decltype std forward fp std forward std forward std invoke google cloud completionqueue std reference wrapper google cloud internal automaticallycreatedbackgroundthreads automaticallycreatedbackgroundthreads unsigned long operator const lambda google cloud completionqueue google cloud promise google cloud completionqueue std reference wrapper usr bin include c type traits in void std thread execute google cloud internal automaticallycreatedbackgroundthreads automaticallycreatedbackgroundthreads unsigned long operator const lambda google cloud completionqueue google cloud promise google cloud completionqueue std reference wrapper std tuple google cloud internal automaticallycreatedbackgroundthreads automaticallycreatedbackgroundthreads unsigned long operator const lambda google cloud completionqueue google cloud promise google cloud completionqueue std reference wrapper std tuple indices usr bin include c thread in void std thread proxy google cloud internal automaticallycreatedbackgroundthreads automaticallycreatedbackgroundthreads unsigned long operator const lambda google cloud completionqueue google cloud promise google cloud completionqueue std reference wrapper void usr bin include c thread in start thread libc so summary memorysanitizer use of uninitialized value proc self cwd external com github grpc grpc include grpcpp impl codegen metadata map h in grpc internal metadatamap getbinaryerrordetails exiting | 0 |
184,304 | 6,711,869,479 | IssuesEvent | 2017-10-13 06:56:05 | openfoundation/foundation-dependencies | https://api.github.com/repos/openfoundation/foundation-dependencies | opened | check versions of spring/spring-boot/sprint-cloud | component/dependencies priority/P1 | Check versions of spring/spring-boot/sprint-cloud.
1. use spirng4.*, spring-boot 1.*, spring-cloud 1.*
2. make sure no version conflits bwteen them. If any, adjust it. | 1.0 | check versions of spring/spring-boot/sprint-cloud - Check versions of spring/spring-boot/sprint-cloud.
1. use spirng4.*, spring-boot 1.*, spring-cloud 1.*
2. make sure no version conflits bwteen them. If any, adjust it. | non_design | check versions of spring spring boot sprint cloud check versions of spring spring boot sprint cloud use spring boot spring cloud make sure no version conflits bwteen them if any adjust it | 0 |
60,081 | 12,056,370,681 | IssuesEvent | 2020-04-15 14:22:07 | IceCubeOpenSource/skyllh | https://api.github.com/repos/IceCubeOpenSource/skyllh | opened | Make KDE info key names configurable within dataset definition | code style | The file skyllh/core/utils/multidimgridpdf.py contains hard-coded names for the keys of the KDE info pickle dictionary. Those names should be set by the dataset definition to allow for different KDE formats. | 1.0 | Make KDE info key names configurable within dataset definition - The file skyllh/core/utils/multidimgridpdf.py contains hard-coded names for the keys of the KDE info pickle dictionary. Those names should be set by the dataset definition to allow for different KDE formats. | non_design | make kde info key names configurable within dataset definition the file skyllh core utils multidimgridpdf py contains hard coded names for the keys of the kde info pickle dictionary those names should be set by the dataset definition to allow for different kde formats | 0 |
71,014 | 8,614,084,565 | IssuesEvent | 2018-11-19 16:34:18 | lbryio/lbry | https://api.github.com/repos/lbryio/lbry | closed | Solve/design the general approach for making daemon calls asynchronous | Tom's Wishlist area: jsonrpc area: wallet level: 3 needs: exploration needs: tech design type: improvement | @tzarebczan commented on [Tue Aug 15 2017](https://github.com/lbryio/lbry-app/issues/475)
<!--
Thanks for reporting an issue to LBRY and helping us improve!
To make it possible for us to help you, please fill out below information carefully.
Before reporting any issues, please make sure that you're using the latest version.
- App releases: https://github.com/lbryio/lbry-app/releases
- Standalone daemon: https://github.com/lbryio/lbry/releases
We are also available on Slack at https://slack.lbry.io
-->
## The Issue
As a Publisher, when I upload files to LBRY, the current process is fairly uninformative after the Publish button is clicked. There is no indication that the file is being processed or when it's finished uploading (besides the URI being available). This is a bigger issue with larger files as they take some time to upload.
Feel free to add/comment.
## System Configuration
<!-- For the app, this info is in the About section at the bottom of the Help page.
You can include a screenshot instead of typing it out -->
<!-- For the daemon, run:
curl 'http://localhost:5279/lbryapi' --data '{"method":"version"}'
and include the full output -->
- LBRY Daemon version:
- LBRY App version:
- LBRY Installation ID:
- Operating system:
## Anything Else
<!-- Include anything else that does not fit into the above sections -->
## Screenshots
<!-- If a screenshot would help explain the bug, please include one or two here -->
---
@kauffj commented on [Tue Aug 15 2017](https://github.com/lbryio/lbry-app/issues/475#issuecomment-322553552)
This isn't an app issue. If you want, you can re-open on lbryio/lbry as "Make publish and get calls asynchronous"
| 1.0 | Solve/design the general approach for making daemon calls asynchronous - @tzarebczan commented on [Tue Aug 15 2017](https://github.com/lbryio/lbry-app/issues/475)
<!--
Thanks for reporting an issue to LBRY and helping us improve!
To make it possible for us to help you, please fill out below information carefully.
Before reporting any issues, please make sure that you're using the latest version.
- App releases: https://github.com/lbryio/lbry-app/releases
- Standalone daemon: https://github.com/lbryio/lbry/releases
We are also available on Slack at https://slack.lbry.io
-->
## The Issue
As a Publisher, when I upload files to LBRY, the current process is fairly uninformative after the Publish button is clicked. There is no indication that the file is being processed or when it's finished uploading (besides the URI being available). This is a bigger issue with larger files as they take some time to upload.
Feel free to add/comment.
## System Configuration
<!-- For the app, this info is in the About section at the bottom of the Help page.
You can include a screenshot instead of typing it out -->
<!-- For the daemon, run:
curl 'http://localhost:5279/lbryapi' --data '{"method":"version"}'
and include the full output -->
- LBRY Daemon version:
- LBRY App version:
- LBRY Installation ID:
- Operating system:
## Anything Else
<!-- Include anything else that does not fit into the above sections -->
## Screenshots
<!-- If a screenshot would help explain the bug, please include one or two here -->
---
@kauffj commented on [Tue Aug 15 2017](https://github.com/lbryio/lbry-app/issues/475#issuecomment-322553552)
This isn't an app issue. If you want, you can re-open on lbryio/lbry as "Make publish and get calls asynchronous"
| design | solve design the general approach for making daemon calls asynchronous tzarebczan commented on thanks for reporting an issue to lbry and helping us improve to make it possible for us to help you please fill out below information carefully before reporting any issues please make sure that you re using the latest version app releases standalone daemon we are also available on slack at the issue as a publisher when i upload files to lbry the current process is fairly uninformative after the publish button is clicked there is no indication that the file is being processed or when it s finished uploading besides the uri being available this is a bigger issue with larger files as they take some time to upload feel free to add comment system configuration for the app this info is in the about section at the bottom of the help page you can include a screenshot instead of typing it out for the daemon run curl data method version and include the full output lbry daemon version lbry app version lbry installation id operating system anything else screenshots kauffj commented on this isn t an app issue if you want you can re open on lbryio lbry as make publish and get calls asynchronous | 1 |
176,833 | 28,236,313,299 | IssuesEvent | 2023-04-06 01:02:53 | MozillaFoundation/Design | https://api.github.com/repos/MozillaFoundation/Design | opened | [Common Voice] Sub Brand Theme Page | Brand Standards design | Common Voice is shown on https://foundation.mozilla.org/en/docs/design/branding/sub-brands/ as a sub brand but doesn't have a page.
This is a placeholder ticket to create a page that captures Common Voice guidelines and expressions. This may require updating and aligning existing styles to relate to the Foundation branding as well.
| 1.0 | [Common Voice] Sub Brand Theme Page - Common Voice is shown on https://foundation.mozilla.org/en/docs/design/branding/sub-brands/ as a sub brand but doesn't have a page.
This is a placeholder ticket to create a page that captures Common Voice guidelines and expressions. This may require updating and aligning existing styles to relate to the Foundation branding as well.
| design | sub brand theme page common voice is shown on as a sub brand but doesn t have a page this is a placeholder ticket to create a page that captures common voice guidelines and expressions this may require updating and aligning existing styles to relate to the foundation branding as well | 1 |
276,264 | 23,981,944,183 | IssuesEvent | 2022-09-13 15:41:43 | department-of-veterans-affairs/va.gov-cms | https://api.github.com/repos/department-of-veterans-affairs/va.gov-cms | closed | Refactor GitHub Actions | Automated testing ⭐️ Sitewide CMS Quality Assurance | ## Description
These share a lot of steps, variables (e.g. PHP version), etc. Plus they're presumably consuming a lot of resources doing so. Let's refactor our GHAs so they DRY.
## Acceptance Criteria
- [ ] GitHub Actions are well-factored.
| 1.0 | Refactor GitHub Actions - ## Description
These share a lot of steps, variables (e.g. PHP version), etc. Plus they're presumably consuming a lot of resources doing so. Let's refactor our GHAs so they DRY.
## Acceptance Criteria
- [ ] GitHub Actions are well-factored.
| non_design | refactor github actions description these share a lot of steps variables e g php version etc plus they re presumably consuming a lot of resources doing so let s refactor our ghas so they dry acceptance criteria github actions are well factored | 0 |
164,311 | 25,947,651,289 | IssuesEvent | 2022-12-17 06:12:21 | 1nMarket/frontend | https://api.github.com/repos/1nMarket/frontend | closed | [design] post_포스트 작성 UI 스타일 | design🎨 | ## ⭐ 주요 기능
[design] profile_사용자 게시글 리스트 UI 스타일
## 📋 진행사항
- [ ] 이미지 슬라이더 생성
- [ ] 게시글 아이템 생성
- [ ] 게시글 리스트 생성
## 🚨 특이사항
이 외 특이사항을 명시해주세요.
| 1.0 | [design] post_포스트 작성 UI 스타일 - ## ⭐ 주요 기능
[design] profile_사용자 게시글 리스트 UI 스타일
## 📋 진행사항
- [ ] 이미지 슬라이더 생성
- [ ] 게시글 아이템 생성
- [ ] 게시글 리스트 생성
## 🚨 특이사항
이 외 특이사항을 명시해주세요.
| design | post 포스트 작성 ui 스타일 ⭐ 주요 기능 profile 사용자 게시글 리스트 ui 스타일 📋 진행사항 이미지 슬라이더 생성 게시글 아이템 생성 게시글 리스트 생성 🚨 특이사항 이 외 특이사항을 명시해주세요 | 1 |
75,329 | 9,221,704,629 | IssuesEvent | 2019-03-11 20:40:59 | TNRIS/data.tnris.org | https://api.github.com/repos/TNRIS/data.tnris.org | closed | Remake Imagery | Design Ideas | These are imagery datasets we need to remake image samples for. Will add more in comments
- [ ] CapArea-McLennan Imagery 2018, Just need a couple more higher rez examples, https://data.tnris.org/collection/22493b55-6c57-4840-aa86-d59c54b00880
SPECS
- 3000px wide
- 1687px high
- 300dpi if possible | 1.0 | Remake Imagery - These are imagery datasets we need to remake image samples for. Will add more in comments
- [ ] CapArea-McLennan Imagery 2018, Just need a couple more higher rez examples, https://data.tnris.org/collection/22493b55-6c57-4840-aa86-d59c54b00880
SPECS
- 3000px wide
- 1687px high
- 300dpi if possible | design | remake imagery these are imagery datasets we need to remake image samples for will add more in comments caparea mclennan imagery just need a couple more higher rez examples specs wide high if possible | 1 |
70,647 | 13,520,088,710 | IssuesEvent | 2020-09-15 03:46:25 | HakinCodes/Malaria-Detection | https://api.github.com/repos/HakinCodes/Malaria-Detection | closed | Create an EDA Documentation Summary | Assigned CH20 Medium No-Code Urgent enhancement | ## Type
Advancement
## Description
@kritikaparmar-programmer has done an excellent job in creating an EDA on the Malarial Cell Dataset. We need a Markdown Documentation that can help us form our Wiki later using the EDA contributed by her. You can check out the Pull Request [here](https://github.com/HakinCodes/Malaria-Detection/pull/48) and create basic documentation to explore the basic intuition behind the Dataset.
## Tools
- Markdown
### Have you read the [Contributing Guidelines on Pull Requests](https://github.com/HakinCodes/Malaria-Detection/blob/master/CONTRIBUTING.md)?
Yes
### Motivation
To later form part of our Wiki
<!-- please delete options that are not relavant -->
| 1.0 | Create an EDA Documentation Summary - ## Type
Advancement
## Description
@kritikaparmar-programmer has done an excellent job in creating an EDA on the Malarial Cell Dataset. We need a Markdown Documentation that can help us form our Wiki later using the EDA contributed by her. You can check out the Pull Request [here](https://github.com/HakinCodes/Malaria-Detection/pull/48) and create basic documentation to explore the basic intuition behind the Dataset.
## Tools
- Markdown
### Have you read the [Contributing Guidelines on Pull Requests](https://github.com/HakinCodes/Malaria-Detection/blob/master/CONTRIBUTING.md)?
Yes
### Motivation
To later form part of our Wiki
<!-- please delete options that are not relavant -->
| non_design | create an eda documentation summary type advancement description kritikaparmar programmer has done an excellent job in creating an eda on the malarial cell dataset we need a markdown documentation that can help us form our wiki later using the eda contributed by her you can check out the pull request and create basic documentation to explore the basic intuition behind the dataset tools markdown have you read the yes motivation to later form part of our wiki | 0 |
72,062 | 18,984,995,359 | IssuesEvent | 2021-11-21 15:12:16 | Seddryck/NBi | https://api.github.com/repos/Seddryck/NBi | opened | Using roapi to serve tests dependant of REST calls | build dependencies | For integration and acceptance tests, we're using some external websites to respond to our API calls. Unfortunately, these external API are evolving or the content returned is also evolving making it difficult to test. Usage of [Roapi](http://github.com/roapi/roapi) would allow us to define our datafiles for testing. | 1.0 | Using roapi to serve tests dependant of REST calls - For integration and acceptance tests, we're using some external websites to respond to our API calls. Unfortunately, these external API are evolving or the content returned is also evolving making it difficult to test. Usage of [Roapi](http://github.com/roapi/roapi) would allow us to define our datafiles for testing. | non_design | using roapi to serve tests dependant of rest calls for integration and acceptance tests we re using some external websites to respond to our api calls unfortunately these external api are evolving or the content returned is also evolving making it difficult to test usage of would allow us to define our datafiles for testing | 0 |
163,302 | 25,787,349,576 | IssuesEvent | 2022-12-09 22:05:31 | cisagov/getgov | https://api.github.com/repos/cisagov/getgov | closed | Goal: Identify and Develop First Draft Educational Content for First-Time Registrants for Login and Domain Requirements/Eligibility | sprint goal design content | Our goal is to understand the path from arriving at get.gov through to starting an application. This requires content and strategy around what a user needs to know and understand prior to hitting "Apply"
- [x] #181
- [ ] #242
- [x] #243
- [x] #249
Outcome: Content for Domain Requirements/Eligibility has been reviewed and any needed supplementary login.gov content has been identified. | 1.0 | Goal: Identify and Develop First Draft Educational Content for First-Time Registrants for Login and Domain Requirements/Eligibility - Our goal is to understand the path from arriving at get.gov through to starting an application. This requires content and strategy around what a user needs to know and understand prior to hitting "Apply"
- [x] #181
- [ ] #242
- [x] #243
- [x] #249
Outcome: Content for Domain Requirements/Eligibility has been reviewed and any needed supplementary login.gov content has been identified. | design | goal identify and develop first draft educational content for first time registrants for login and domain requirements eligibility our goal is to understand the path from arriving at get gov through to starting an application this requires content and strategy around what a user needs to know and understand prior to hitting apply outcome content for domain requirements eligibility has been reviewed and any needed supplementary login gov content has been identified | 1 |
46,423 | 13,168,670,881 | IssuesEvent | 2020-08-11 12:32:29 | michalmit/WebGoat | https://api.github.com/repos/michalmit/WebGoat | opened | CVE-2018-20822 (Medium) detected in node-sass-4.11.0.tgz, opennms-opennms-source-22.0.1-1 | security vulnerability | ## CVE-2018-20822 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.11.0.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.11.0.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.11.0.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.11.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/WebGoat/docs/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/WebGoat/docs/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- gulp-sass-4.0.2.tgz (Root Library)
- :x: **node-sass-4.11.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/michalmit/WebGoat/commit/ded1b7835a3e213e2329b24fe61829370add2ea7">ded1b7835a3e213e2329b24fe61829370add2ea7</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
LibSass 3.5.4 allows attackers to cause a denial-of-service (uncontrolled recursion in Sass::Complex_Selector::perform in ast.hpp and Sass::Inspect::operator in inspect.cpp).
<p>Publish Date: 2019-04-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20822>CVE-2018-20822</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20822">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20822</a></p>
<p>Release Date: 2019-08-06</p>
<p>Fix Resolution: LibSass - 3.6.0;node-sass - 4.13.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-sass","packageVersion":"4.11.0","isTransitiveDependency":true,"dependencyTree":"gulp-sass:4.0.2;node-sass:4.11.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"LibSass - 3.6.0;node-sass - 4.13.1"}],"vulnerabilityIdentifier":"CVE-2018-20822","vulnerabilityDetails":"LibSass 3.5.4 allows attackers to cause a denial-of-service (uncontrolled recursion in Sass::Complex_Selector::perform in ast.hpp and Sass::Inspect::operator in inspect.cpp).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20822","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2018-20822 (Medium) detected in node-sass-4.11.0.tgz, opennms-opennms-source-22.0.1-1 - ## CVE-2018-20822 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.11.0.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.11.0.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.11.0.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.11.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/WebGoat/docs/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/WebGoat/docs/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- gulp-sass-4.0.2.tgz (Root Library)
- :x: **node-sass-4.11.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/michalmit/WebGoat/commit/ded1b7835a3e213e2329b24fe61829370add2ea7">ded1b7835a3e213e2329b24fe61829370add2ea7</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
LibSass 3.5.4 allows attackers to cause a denial-of-service (uncontrolled recursion in Sass::Complex_Selector::perform in ast.hpp and Sass::Inspect::operator in inspect.cpp).
<p>Publish Date: 2019-04-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20822>CVE-2018-20822</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20822">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20822</a></p>
<p>Release Date: 2019-08-06</p>
<p>Fix Resolution: LibSass - 3.6.0;node-sass - 4.13.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-sass","packageVersion":"4.11.0","isTransitiveDependency":true,"dependencyTree":"gulp-sass:4.0.2;node-sass:4.11.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"LibSass - 3.6.0;node-sass - 4.13.1"}],"vulnerabilityIdentifier":"CVE-2018-20822","vulnerabilityDetails":"LibSass 3.5.4 allows attackers to cause a denial-of-service (uncontrolled recursion in Sass::Complex_Selector::perform in ast.hpp and Sass::Inspect::operator in inspect.cpp).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20822","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_design | cve medium detected in node sass tgz opennms opennms source cve medium severity vulnerability vulnerable libraries node sass tgz node sass tgz wrapper around libsass library home page a href path to dependency file tmp ws scm webgoat docs package json path to vulnerable library tmp ws scm webgoat docs node modules node sass package json dependency hierarchy gulp sass tgz root library x node sass tgz vulnerable library found in head commit a href vulnerability details libsass allows attackers to cause a denial of service uncontrolled recursion in sass complex selector perform in ast hpp and sass inspect operator in inspect cpp publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution libsass node sass isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails libsass allows attackers to cause a denial of service uncontrolled recursion in sass complex selector perform in ast hpp and sass inspect operator in inspect cpp vulnerabilityurl | 0 |
161,383 | 20,149,274,454 | IssuesEvent | 2022-02-09 10:43:46 | NormanWenzelWSS/WebGoat | https://api.github.com/repos/NormanWenzelWSS/WebGoat | opened | xstream-1.4.5.jar: 33 vulnerabilities (highest severity is: 9.9) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.5.jar</b></p></summary>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/NormanWenzelWSS/WebGoat/commit/8dd63d1de0434feeb3b6657bd9b7e36f033023f9">8dd63d1de0434feeb3b6657bd9b7e36f033023f9</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-21345](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21345) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.9 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21344](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21344) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2013-7285](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-7285) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | xstream-1.4.5.jar | Direct | 1.4.7,1.4.11 | ✅ |
| [CVE-2021-21350](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21350) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21347](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21347) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21346](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21346) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21342](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21342) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.1 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21351](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21351) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.1 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-39139](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39139) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2020-26217](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26217) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.14 | ✅ |
| [CVE-2021-29505](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29505) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.17 | ✅ |
| [CVE-2021-21349](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21349) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.6 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-39150](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39150) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39152](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39152) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39151](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39151) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39154](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39154) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39153](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39153) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39141](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39141) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39145](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39145) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39144](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39144) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39147](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39147) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39146](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39146) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39149](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39149) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39148](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39148) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2020-26258](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26258) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.7 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.15 | ✅ |
| [CVE-2021-21343](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21343) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21341](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21341) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2017-7957](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7957) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | 1.4.10 | ✅ |
| [CVE-2016-3674](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-3674) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | 1.4.9 | ✅ |
| [CVE-2021-43859](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43859) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.19 | ✅ |
| [CVE-2021-21348](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21348) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2020-26259](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26259) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.15 | ✅ |
| [CVE-2021-39140](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39140) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.3 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
## Details
> Partial details (5 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the WhiteSource Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-21345</summary>
### Vulnerable Library - <b>xstream-1.4.5.jar</b></p>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/NormanWenzelWSS/WebGoat/commit/8dd63d1de0434feeb3b6657bd9b7e36f033023f9">8dd63d1de0434feeb3b6657bd9b7e36f033023f9</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker who has sufficient rights to execute commands of the host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream's security framework with a whitelist limited to the minimal required types. If you rely on XStream's default blacklist of the Security Framework, you will have to use at least version 1.4.16.
<p>Publish Date: 2021-03-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21345>CVE-2021-21345</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/x-stream/xstream/security/advisories/GHSA-hwpc-8xqv-jvj4">https://github.com/x-stream/xstream/security/advisories/GHSA-hwpc-8xqv-jvj4</a></p>
<p>Release Date: 2021-03-23</p>
<p>Fix Resolution: com.thoughtworks.xstream:xstream:1.4.16</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-21344</summary>
### Vulnerable Library - <b>xstream-1.4.5.jar</b></p>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/NormanWenzelWSS/WebGoat/commit/8dd63d1de0434feeb3b6657bd9b7e36f033023f9">8dd63d1de0434feeb3b6657bd9b7e36f033023f9</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream's security framework with a whitelist limited to the minimal required types. If you rely on XStream's default blacklist of the Security Framework, you will have to use at least version 1.4.16.
<p>Publish Date: 2021-03-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21344>CVE-2021-21344</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/x-stream/xstream/security/advisories/GHSA-59jw-jqf4-3wq3">https://github.com/x-stream/xstream/security/advisories/GHSA-59jw-jqf4-3wq3</a></p>
<p>Release Date: 2021-03-23</p>
<p>Fix Resolution: com.thoughtworks.xstream:xstream:1.4.16</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2013-7285</summary>
### Vulnerable Library - <b>xstream-1.4.5.jar</b></p>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/NormanWenzelWSS/WebGoat/commit/8dd63d1de0434feeb3b6657bd9b7e36f033023f9">8dd63d1de0434feeb3b6657bd9b7e36f033023f9</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Xstream API versions up to 1.4.6 and version 1.4.10, if the security framework has not been initialized, may allow a remote attacker to run arbitrary shell commands by manipulating the processed input stream when unmarshaling XML or any supported format. e.g. JSON.
<p>Publish Date: 2019-05-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-7285>CVE-2013-7285</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-7285">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-7285</a></p>
<p>Release Date: 2019-05-15</p>
<p>Fix Resolution: 1.4.7,1.4.11</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-21350</summary>
### Vulnerable Library - <b>xstream-1.4.5.jar</b></p>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/NormanWenzelWSS/WebGoat/commit/8dd63d1de0434feeb3b6657bd9b7e36f033023f9">8dd63d1de0434feeb3b6657bd9b7e36f033023f9</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to execute arbitrary code only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream's security framework with a whitelist limited to the minimal required types. If you rely on XStream's default blacklist of the Security Framework, you will have to use at least version 1.4.16.
<p>Publish Date: 2021-03-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21350>CVE-2021-21350</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/x-stream/xstream/security/advisories/GHSA-43gc-mjxg-gvrq">https://github.com/x-stream/xstream/security/advisories/GHSA-43gc-mjxg-gvrq</a></p>
<p>Release Date: 2021-03-23</p>
<p>Fix Resolution: com.thoughtworks.xstream:xstream:1.4.16</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-21347</summary>
### Vulnerable Library - <b>xstream-1.4.5.jar</b></p>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/NormanWenzelWSS/WebGoat/commit/8dd63d1de0434feeb3b6657bd9b7e36f033023f9">8dd63d1de0434feeb3b6657bd9b7e36f033023f9</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream's security framework with a whitelist limited to the minimal required types. If you rely on XStream's default blacklist of the Security Framework, you will have to use at least version 1.4.16.
<p>Publish Date: 2021-03-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21347>CVE-2021-21347</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/x-stream/xstream/security/advisories/GHSA-qpfq-ph7r-qv6f">https://github.com/x-stream/xstream/security/advisories/GHSA-qpfq-ph7r-qv6f</a></p>
<p>Release Date: 2021-03-23</p>
<p>Fix Resolution: com.thoughtworks.xstream:xstream:1.4.16</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21345","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker who has sufficient rights to execute commands of the host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21345","cvss3Severity":"high","cvss3Score":"9.9","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21344","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21344","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.4.7,1.4.11","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2013-7285","vulnerabilityDetails":"Xstream API versions up to 1.4.6 and version 1.4.10, if the security framework has not been initialized, may allow a remote attacker to run arbitrary shell commands by manipulating the processed input stream when unmarshaling XML or any supported format. e.g. JSON.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-7285","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21350","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to execute arbitrary code only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21350","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21347","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21347","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21346","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21346","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21342","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability where the processed stream at unmarshalling time contains type information to recreate the formerly written objects. XStream creates therefore new instances based on these type information. An attacker can manipulate the processed input stream and replace or inject objects, that result in a server-side forgery request. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21342","cvss3Severity":"high","cvss3Score":"9.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21351","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21351","cvss3Severity":"high","cvss3Score":"9.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39139","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. A user is only affected if using the version out of the box with JDK 1.7u21 or below. However, this scenario can be adjusted easily to an external Xalan that works regardless of the version of the Java runtime. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39139","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.14","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2020-26217","vulnerabilityDetails":"XStream before version 1.4.14 is vulnerable to Remote Code Execution.The vulnerability may allow a remote attacker to run arbitrary shell commands only by manipulating the processed input stream. Only users who rely on blocklists are affected. Anyone using XStream\u0027s Security Framework allowlist is not affected. The linked advisory provides code workarounds for users who cannot upgrade. The issue is fixed in version 1.4.14.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26217","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.17","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-29505","vulnerabilityDetails":"XStream is software for serializing Java objects to XML and back again. A vulnerability in XStream versions prior to 1.4.17 may allow a remote attacker has sufficient rights to execute commands of the host only by manipulating the processed input stream. No user who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types is affected. The vulnerability is patched in version 1.4.17.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29505","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21349","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21349","cvss3Severity":"high","cvss3Score":"8.6","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39150","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream with a Java runtime version 14 to 8. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the [Security Framework](https://x-stream.github.io/security.html#framework), you will have to use at least version 1.4.18.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39150","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39152","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream with a Java runtime version 14 to 8. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the [Security Framework](https://x-stream.github.io/security.html#framework), you will have to use at least version 1.4.18.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39152","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39151","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39151","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39154","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39154","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39153","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream, if using the version out of the box with Java runtime version 14 to 8 or with JavaFX installed. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39153","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39141","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39141","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39145","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39145","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39144","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker has sufficient rights to execute commands of the host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39144","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39147","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39147","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39146","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39146","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39149","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39149","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39148","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39148","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.15","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2020-26258","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.15, a Server-Side Forgery Request vulnerability can be activated when unmarshalling. The vulnerability may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.15. The reported vulnerability does not exist if running Java 15 or higher. No user is affected who followed the recommendation to setup XStream\u0027s Security Framework with a whitelist! Anyone relying on XStream\u0027s default blacklist can immediately switch to a whilelist for the allowed types to avoid the vulnerability. Users of XStream 1.4.14 or below who still want to use XStream default blacklist can use a workaround described in more detailed in the referenced advisories.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26258","cvss3Severity":"high","cvss3Score":"7.7","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21343","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability where the processed stream at unmarshalling time contains type information to recreate the formerly written objects. XStream creates therefore new instances based on these type information. An attacker can manipulate the processed input stream and replace or inject objects, that result in the deletion of a file on the local host. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21343","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21341","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is vulnerability which may allow a remote attacker to allocate 100% CPU time on the target system depending on CPU type or parallel execution of such a payload resulting in a denial of service only by manipulating the processed input stream. No user is affected who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21341","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.4.10","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2017-7957","vulnerabilityDetails":"XStream through 1.4.9, when a certain denyTypes workaround is not used, mishandles attempts to create an instance of the primitive type \u0027void\u0027 during unmarshalling, leading to a remote application crash, as demonstrated by an xstream.fromXML(\"\u003cvoid/\u003e\") call.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7957","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.4.9","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2016-3674","vulnerabilityDetails":"Multiple XML external entity (XXE) vulnerabilities in the (1) Dom4JDriver, (2) DomDriver, (3) JDomDriver, (4) JDom2Driver, (5) SjsxpDriver, (6) StandardStaxDriver, and (7) WstxDriver drivers in XStream before 1.4.9 allow remote attackers to read arbitrary files via a crafted XML document.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-3674","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.19","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-43859","vulnerabilityDetails":"XStream is an open source java library to serialize objects to XML and back again. Versions prior to 1.4.19 may allow a remote attacker to allocate 100% CPU time on the target system depending on CPU type or parallel execution of such a payload resulting in a denial of service only by manipulating the processed input stream. XStream 1.4.19 monitors and accumulates the time it takes to add elements to collections and throws an exception if a set threshold is exceeded. Users are advised to upgrade as soon as possible. Users unable to upgrade may set the NO_REFERENCE mode to prevent recursion. See GHSA-rmr5-cpv2-vgjf for further details on a workaround if an upgrade is not possible.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43859","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21348","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to occupy a thread that consumes maximum CPU time and will never return. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21348","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.15","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2020-26259","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.15, is vulnerable to an Arbitrary File Deletion on the local host when unmarshalling. The vulnerability may allow a remote attacker to delete arbitrary know files on the host as log as the executing process has sufficient rights only by manipulating the processed input stream. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.15. The reported vulnerability does not exist running Java 15 or higher. No user is affected, who followed the recommendation to setup XStream\u0027s Security Framework with a whitelist! Anyone relying on XStream\u0027s default blacklist can immediately switch to a whilelist for the allowed types to avoid the vulnerability. Users of XStream 1.4.14 or below who still want to use XStream default blacklist can use a workaround described in more detailed in the referenced advisories.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26259","cvss3Severity":"medium","cvss3Score":"6.8","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Changed","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39140","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to allocate 100% CPU time on the target system depending on CPU type or parallel execution of such a payload resulting in a denial of service only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39140","cvss3Severity":"medium","cvss3Score":"6.3","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}]</REMEDIATE> --> | True | xstream-1.4.5.jar: 33 vulnerabilities (highest severity is: 9.9) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.5.jar</b></p></summary>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/NormanWenzelWSS/WebGoat/commit/8dd63d1de0434feeb3b6657bd9b7e36f033023f9">8dd63d1de0434feeb3b6657bd9b7e36f033023f9</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-21345](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21345) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.9 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21344](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21344) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2013-7285](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-7285) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | xstream-1.4.5.jar | Direct | 1.4.7,1.4.11 | ✅ |
| [CVE-2021-21350](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21350) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21347](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21347) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21346](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21346) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21342](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21342) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.1 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21351](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21351) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.1 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-39139](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39139) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2020-26217](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26217) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.14 | ✅ |
| [CVE-2021-29505](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29505) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.17 | ✅ |
| [CVE-2021-21349](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21349) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.6 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-39150](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39150) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39152](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39152) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39151](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39151) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39154](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39154) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39153](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39153) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39141](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39141) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39145](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39145) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39144](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39144) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39147](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39147) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39146](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39146) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39149](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39149) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2021-39148](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39148) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
| [CVE-2020-26258](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26258) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.7 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.15 | ✅ |
| [CVE-2021-21343](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21343) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2021-21341](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21341) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2017-7957](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7957) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | 1.4.10 | ✅ |
| [CVE-2016-3674](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-3674) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | 1.4.9 | ✅ |
| [CVE-2021-43859](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43859) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.19 | ✅ |
| [CVE-2021-21348](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21348) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.16 | ✅ |
| [CVE-2020-26259](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26259) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.8 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.15 | ✅ |
| [CVE-2021-39140](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39140) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.3 | xstream-1.4.5.jar | Direct | com.thoughtworks.xstream:xstream:1.4.18 | ✅ |
## Details
> Partial details (5 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the WhiteSource Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-21345</summary>
### Vulnerable Library - <b>xstream-1.4.5.jar</b></p>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/NormanWenzelWSS/WebGoat/commit/8dd63d1de0434feeb3b6657bd9b7e36f033023f9">8dd63d1de0434feeb3b6657bd9b7e36f033023f9</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker who has sufficient rights to execute commands of the host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream's security framework with a whitelist limited to the minimal required types. If you rely on XStream's default blacklist of the Security Framework, you will have to use at least version 1.4.16.
<p>Publish Date: 2021-03-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21345>CVE-2021-21345</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/x-stream/xstream/security/advisories/GHSA-hwpc-8xqv-jvj4">https://github.com/x-stream/xstream/security/advisories/GHSA-hwpc-8xqv-jvj4</a></p>
<p>Release Date: 2021-03-23</p>
<p>Fix Resolution: com.thoughtworks.xstream:xstream:1.4.16</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-21344</summary>
### Vulnerable Library - <b>xstream-1.4.5.jar</b></p>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/NormanWenzelWSS/WebGoat/commit/8dd63d1de0434feeb3b6657bd9b7e36f033023f9">8dd63d1de0434feeb3b6657bd9b7e36f033023f9</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream's security framework with a whitelist limited to the minimal required types. If you rely on XStream's default blacklist of the Security Framework, you will have to use at least version 1.4.16.
<p>Publish Date: 2021-03-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21344>CVE-2021-21344</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/x-stream/xstream/security/advisories/GHSA-59jw-jqf4-3wq3">https://github.com/x-stream/xstream/security/advisories/GHSA-59jw-jqf4-3wq3</a></p>
<p>Release Date: 2021-03-23</p>
<p>Fix Resolution: com.thoughtworks.xstream:xstream:1.4.16</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2013-7285</summary>
### Vulnerable Library - <b>xstream-1.4.5.jar</b></p>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/NormanWenzelWSS/WebGoat/commit/8dd63d1de0434feeb3b6657bd9b7e36f033023f9">8dd63d1de0434feeb3b6657bd9b7e36f033023f9</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Xstream API versions up to 1.4.6 and version 1.4.10, if the security framework has not been initialized, may allow a remote attacker to run arbitrary shell commands by manipulating the processed input stream when unmarshaling XML or any supported format. e.g. JSON.
<p>Publish Date: 2019-05-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-7285>CVE-2013-7285</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-7285">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-7285</a></p>
<p>Release Date: 2019-05-15</p>
<p>Fix Resolution: 1.4.7,1.4.11</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-21350</summary>
### Vulnerable Library - <b>xstream-1.4.5.jar</b></p>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/NormanWenzelWSS/WebGoat/commit/8dd63d1de0434feeb3b6657bd9b7e36f033023f9">8dd63d1de0434feeb3b6657bd9b7e36f033023f9</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to execute arbitrary code only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream's security framework with a whitelist limited to the minimal required types. If you rely on XStream's default blacklist of the Security Framework, you will have to use at least version 1.4.16.
<p>Publish Date: 2021-03-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21350>CVE-2021-21350</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/x-stream/xstream/security/advisories/GHSA-43gc-mjxg-gvrq">https://github.com/x-stream/xstream/security/advisories/GHSA-43gc-mjxg-gvrq</a></p>
<p>Release Date: 2021-03-23</p>
<p>Fix Resolution: com.thoughtworks.xstream:xstream:1.4.16</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-21347</summary>
### Vulnerable Library - <b>xstream-1.4.5.jar</b></p>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/NormanWenzelWSS/WebGoat/commit/8dd63d1de0434feeb3b6657bd9b7e36f033023f9">8dd63d1de0434feeb3b6657bd9b7e36f033023f9</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream's security framework with a whitelist limited to the minimal required types. If you rely on XStream's default blacklist of the Security Framework, you will have to use at least version 1.4.16.
<p>Publish Date: 2021-03-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21347>CVE-2021-21347</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/x-stream/xstream/security/advisories/GHSA-qpfq-ph7r-qv6f">https://github.com/x-stream/xstream/security/advisories/GHSA-qpfq-ph7r-qv6f</a></p>
<p>Release Date: 2021-03-23</p>
<p>Fix Resolution: com.thoughtworks.xstream:xstream:1.4.16</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21345","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker who has sufficient rights to execute commands of the host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21345","cvss3Severity":"high","cvss3Score":"9.9","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21344","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21344","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.4.7,1.4.11","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2013-7285","vulnerabilityDetails":"Xstream API versions up to 1.4.6 and version 1.4.10, if the security framework has not been initialized, may allow a remote attacker to run arbitrary shell commands by manipulating the processed input stream when unmarshaling XML or any supported format. e.g. JSON.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-7285","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21350","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to execute arbitrary code only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21350","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21347","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21347","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21346","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21346","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21342","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability where the processed stream at unmarshalling time contains type information to recreate the formerly written objects. XStream creates therefore new instances based on these type information. An attacker can manipulate the processed input stream and replace or inject objects, that result in a server-side forgery request. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21342","cvss3Severity":"high","cvss3Score":"9.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21351","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21351","cvss3Severity":"high","cvss3Score":"9.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39139","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. A user is only affected if using the version out of the box with JDK 1.7u21 or below. However, this scenario can be adjusted easily to an external Xalan that works regardless of the version of the Java runtime. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39139","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.14","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2020-26217","vulnerabilityDetails":"XStream before version 1.4.14 is vulnerable to Remote Code Execution.The vulnerability may allow a remote attacker to run arbitrary shell commands only by manipulating the processed input stream. Only users who rely on blocklists are affected. Anyone using XStream\u0027s Security Framework allowlist is not affected. The linked advisory provides code workarounds for users who cannot upgrade. The issue is fixed in version 1.4.14.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26217","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.17","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-29505","vulnerabilityDetails":"XStream is software for serializing Java objects to XML and back again. A vulnerability in XStream versions prior to 1.4.17 may allow a remote attacker has sufficient rights to execute commands of the host only by manipulating the processed input stream. No user who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types is affected. The vulnerability is patched in version 1.4.17.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29505","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21349","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21349","cvss3Severity":"high","cvss3Score":"8.6","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39150","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream with a Java runtime version 14 to 8. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the [Security Framework](https://x-stream.github.io/security.html#framework), you will have to use at least version 1.4.18.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39150","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39152","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream with a Java runtime version 14 to 8. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the [Security Framework](https://x-stream.github.io/security.html#framework), you will have to use at least version 1.4.18.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39152","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39151","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39151","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39154","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39154","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39153","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream, if using the version out of the box with Java runtime version 14 to 8 or with JavaFX installed. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39153","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39141","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39141","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39145","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39145","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39144","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker has sufficient rights to execute commands of the host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39144","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39147","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39147","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39146","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39146","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39149","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39149","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39148","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39148","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.15","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2020-26258","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.15, a Server-Side Forgery Request vulnerability can be activated when unmarshalling. The vulnerability may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.15. The reported vulnerability does not exist if running Java 15 or higher. No user is affected who followed the recommendation to setup XStream\u0027s Security Framework with a whitelist! Anyone relying on XStream\u0027s default blacklist can immediately switch to a whilelist for the allowed types to avoid the vulnerability. Users of XStream 1.4.14 or below who still want to use XStream default blacklist can use a workaround described in more detailed in the referenced advisories.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26258","cvss3Severity":"high","cvss3Score":"7.7","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21343","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability where the processed stream at unmarshalling time contains type information to recreate the formerly written objects. XStream creates therefore new instances based on these type information. An attacker can manipulate the processed input stream and replace or inject objects, that result in the deletion of a file on the local host. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21343","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21341","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is vulnerability which may allow a remote attacker to allocate 100% CPU time on the target system depending on CPU type or parallel execution of such a payload resulting in a denial of service only by manipulating the processed input stream. No user is affected who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21341","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.4.10","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2017-7957","vulnerabilityDetails":"XStream through 1.4.9, when a certain denyTypes workaround is not used, mishandles attempts to create an instance of the primitive type \u0027void\u0027 during unmarshalling, leading to a remote application crash, as demonstrated by an xstream.fromXML(\"\u003cvoid/\u003e\") call.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7957","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.4.9","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2016-3674","vulnerabilityDetails":"Multiple XML external entity (XXE) vulnerabilities in the (1) Dom4JDriver, (2) DomDriver, (3) JDomDriver, (4) JDom2Driver, (5) SjsxpDriver, (6) StandardStaxDriver, and (7) WstxDriver drivers in XStream before 1.4.9 allow remote attackers to read arbitrary files via a crafted XML document.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-3674","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.19","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-43859","vulnerabilityDetails":"XStream is an open source java library to serialize objects to XML and back again. Versions prior to 1.4.19 may allow a remote attacker to allocate 100% CPU time on the target system depending on CPU type or parallel execution of such a payload resulting in a denial of service only by manipulating the processed input stream. XStream 1.4.19 monitors and accumulates the time it takes to add elements to collections and throws an exception if a set threshold is exceeded. Users are advised to upgrade as soon as possible. Users unable to upgrade may set the NO_REFERENCE mode to prevent recursion. See GHSA-rmr5-cpv2-vgjf for further details on a workaround if an upgrade is not possible.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43859","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.16","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-21348","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to occupy a thread that consumes maximum CPU time and will never return. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.16.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21348","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.15","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2020-26259","vulnerabilityDetails":"XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.15, is vulnerable to an Arbitrary File Deletion on the local host when unmarshalling. The vulnerability may allow a remote attacker to delete arbitrary know files on the host as log as the executing process has sufficient rights only by manipulating the processed input stream. If you rely on XStream\u0027s default blacklist of the Security Framework, you will have to use at least version 1.4.15. The reported vulnerability does not exist running Java 15 or higher. No user is affected, who followed the recommendation to setup XStream\u0027s Security Framework with a whitelist! Anyone relying on XStream\u0027s default blacklist can immediately switch to a whilelist for the allowed types to avoid the vulnerability. Users of XStream 1.4.14 or below who still want to use XStream default blacklist can use a workaround described in more detailed in the referenced advisories.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26259","cvss3Severity":"medium","cvss3Score":"6.8","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Changed","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.thoughtworks.xstream","packageName":"xstream","packageVersion":"1.4.5","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"com.thoughtworks.xstream:xstream:1.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.thoughtworks.xstream:xstream:1.4.18","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-39140","vulnerabilityDetails":"XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to allocate 100% CPU time on the target system depending on CPU type or parallel execution of such a payload resulting in a denial of service only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream\u0027s security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39140","cvss3Severity":"medium","cvss3Score":"6.3","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}]</REMEDIATE> --> | non_design | xstream jar vulnerabilities highest severity is vulnerable library xstream jar xstream is a serialization library from java objects to xml and back found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct ✅ high xstream jar direct ✅ high xstream jar direct com thoughtworks xstream xstream ✅ high xstream jar direct com thoughtworks xstream xstream ✅ medium xstream jar direct com thoughtworks xstream xstream ✅ medium xstream jar direct com thoughtworks xstream xstream ✅ details partial details vulnerabilities are displayed below due to a content size limitation in github to view information on the remaining vulnerabilities navigate to the whitesource application cve vulnerable library xstream jar xstream is a serialization library from java objects to xml and back dependency hierarchy x xstream jar vulnerable library found in head commit a href found in base branch develop vulnerability details xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker who has sufficient rights to execute commands of the host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream s security framework with a whitelist limited to the minimal required types if you rely on xstream s default blacklist of the security framework you will have to use at least version publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com thoughtworks xstream xstream rescue worker helmet automatic remediation is available for this issue cve vulnerable library xstream jar xstream is a serialization library from java objects to xml and back dependency hierarchy x xstream jar vulnerable library found in head commit a href found in base branch develop vulnerability details xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream s security framework with a whitelist limited to the minimal required types if you rely on xstream s default blacklist of the security framework you will have to use at least version publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com thoughtworks xstream xstream rescue worker helmet automatic remediation is available for this issue cve vulnerable library xstream jar xstream is a serialization library from java objects to xml and back dependency hierarchy x xstream jar vulnerable library found in head commit a href found in base branch develop vulnerability details xstream api versions up to and version if the security framework has not been initialized may allow a remote attacker to run arbitrary shell commands by manipulating the processed input stream when unmarshaling xml or any supported format e g json publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library xstream jar xstream is a serialization library from java objects to xml and back dependency hierarchy x xstream jar vulnerable library found in head commit a href found in base branch develop vulnerability details xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker to execute arbitrary code only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream s security framework with a whitelist limited to the minimal required types if you rely on xstream s default blacklist of the security framework you will have to use at least version publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com thoughtworks xstream xstream rescue worker helmet automatic remediation is available for this issue cve vulnerable library xstream jar xstream is a serialization library from java objects to xml and back dependency hierarchy x xstream jar vulnerable library found in head commit a href found in base branch develop vulnerability details xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream s security framework with a whitelist limited to the minimal required types if you rely on xstream s default blacklist of the security framework you will have to use at least version publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com thoughtworks xstream xstream rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker who has sufficient rights to execute commands of the host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream api versions up to and version if the security framework has not been initialized may allow a remote attacker to run arbitrary shell commands by manipulating the processed input stream when unmarshaling xml or any supported format e g json vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker to execute arbitrary code only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability where the processed stream at unmarshalling time contains type information to recreate the formerly written objects xstream creates therefore new instances based on these type information an attacker can manipulate the processed input stream and replace or inject objects that result in a server side forgery request no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream a user is only affected if using the version out of the box with jdk or below however this scenario can be adjusted easily to an external xalan that works regardless of the version of the java runtime no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream before version is vulnerable to remote code execution the vulnerability may allow a remote attacker to run arbitrary shell commands only by manipulating the processed input stream only users who rely on blocklists are affected anyone using xstream security framework allowlist is not affected the linked advisory provides code workarounds for users who cannot upgrade the issue is fixed in version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is software for serializing java objects to xml and back again a vulnerability in xstream versions prior to may allow a remote attacker has sufficient rights to execute commands of the host only by manipulating the processed input stream no user who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types is affected the vulnerability is patched in version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream with a java runtime version to no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream with a java runtime version to no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream if using the version out of the box with java runtime version to or with javafx installed no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker has sufficient rights to execute commands of the host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version a server side forgery request vulnerability can be activated when unmarshalling the vulnerability may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream if you rely on xstream default blacklist of the security framework you will have to use at least version the reported vulnerability does not exist if running java or higher no user is affected who followed the recommendation to setup xstream security framework with a whitelist anyone relying on xstream default blacklist can immediately switch to a whilelist for the allowed types to avoid the vulnerability users of xstream or below who still want to use xstream default blacklist can use a workaround described in more detailed in the referenced advisories vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability where the processed stream at unmarshalling time contains type information to recreate the formerly written objects xstream creates therefore new instances based on these type information an attacker can manipulate the processed input stream and replace or inject objects that result in the deletion of a file on the local host no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is vulnerability which may allow a remote attacker to allocate cpu time on the target system depending on cpu type or parallel execution of such a payload resulting in a denial of service only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream through when a certain denytypes workaround is not used mishandles attempts to create an instance of the primitive type during unmarshalling leading to a remote application crash as demonstrated by an xstream fromxml call vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails multiple xml external entity xxe vulnerabilities in the domdriver jdomdriver sjsxpdriver standardstaxdriver and wstxdriver drivers in xstream before allow remote attackers to read arbitrary files via a crafted xml document vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is an open source java library to serialize objects to xml and back again versions prior to may allow a remote attacker to allocate cpu time on the target system depending on cpu type or parallel execution of such a payload resulting in a denial of service only by manipulating the processed input stream xstream monitors and accumulates the time it takes to add elements to collections and throws an exception if a set threshold is exceeded users are advised to upgrade as soon as possible users unable to upgrade may set the no reference mode to prevent recursion see ghsa vgjf for further details on a workaround if an upgrade is not possible vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker to occupy a thread that consumes maximum cpu time and will never return no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types if you rely on xstream default blacklist of the security framework you will have to use at least version vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a java library to serialize objects to xml and back again in xstream before version is vulnerable to an arbitrary file deletion on the local host when unmarshalling the vulnerability may allow a remote attacker to delete arbitrary know files on the host as log as the executing process has sufficient rights only by manipulating the processed input stream if you rely on xstream default blacklist of the security framework you will have to use at least version the reported vulnerability does not exist running java or higher no user is affected who followed the recommendation to setup xstream security framework with a whitelist anyone relying on xstream default blacklist can immediately switch to a whilelist for the allowed types to avoid the vulnerability users of xstream or below who still want to use xstream default blacklist can use a workaround described in more detailed in the referenced advisories vulnerabilityurl istransitivedependency false dependencytree com thoughtworks xstream xstream isminimumfixversionavailable true minimumfixversion com thoughtworks xstream xstream isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to allocate cpu time on the target system depending on cpu type or parallel execution of such a payload resulting in a denial of service only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose vulnerabilityurl | 0 |
148,815 | 23,386,634,214 | IssuesEvent | 2022-08-11 14:15:39 | MystenLabs/narwhal | https://api.github.com/repos/MystenLabs/narwhal | closed | [consensus] Explicitly order batches coming from the block waiter | good first issue design task task |
### Description
The current block waiter fetches transactions' data in batches in an implicit (but deterministic) order. We should make this order explicit and choose a way to order them. We should also think of the best place to order those batches. | 1.0 | [consensus] Explicitly order batches coming from the block waiter -
### Description
The current block waiter fetches transactions' data in batches in an implicit (but deterministic) order. We should make this order explicit and choose a way to order them. We should also think of the best place to order those batches. | design | explicitly order batches coming from the block waiter description the current block waiter fetches transactions data in batches in an implicit but deterministic order we should make this order explicit and choose a way to order them we should also think of the best place to order those batches | 1 |
86,589 | 24,898,972,520 | IssuesEvent | 2022-10-28 18:42:21 | opensearch-project/OpenSearch-Dashboards | https://api.github.com/repos/opensearch-project/OpenSearch-Dashboards | closed | [D&D] Replace wizard naming convention | vis builder v2.4.0 | Renaming "Wizard" to "Visualization Builder"
Tasks:
In code reference of 'wizard' string:
- [x] Rename `wizard` in code to `visBuilder` in function name, type name and class name
- [x] Replace class name prefixes `wiz` with `vb`
- [x] Replace file name and paths of 'wizard' to 'vis_builder'
- [x] Rename 'wizard' saved object type
UI/UX reference of 'wizard' string: https://github.com/opensearch-project/ux/issues/49
- [x] wizard editing page
- [x] dashboard page
- [x] visualization page
- [x] saved object page | 1.0 | [D&D] Replace wizard naming convention - Renaming "Wizard" to "Visualization Builder"
Tasks:
In code reference of 'wizard' string:
- [x] Rename `wizard` in code to `visBuilder` in function name, type name and class name
- [x] Replace class name prefixes `wiz` with `vb`
- [x] Replace file name and paths of 'wizard' to 'vis_builder'
- [x] Rename 'wizard' saved object type
UI/UX reference of 'wizard' string: https://github.com/opensearch-project/ux/issues/49
- [x] wizard editing page
- [x] dashboard page
- [x] visualization page
- [x] saved object page | non_design | replace wizard naming convention renaming wizard to visualization builder tasks in code reference of wizard string rename wizard in code to visbuilder in function name type name and class name replace class name prefixes wiz with vb replace file name and paths of wizard to vis builder rename wizard saved object type ui ux reference of wizard string wizard editing page dashboard page visualization page saved object page | 0 |
67,074 | 8,072,924,856 | IssuesEvent | 2018-08-06 17:32:44 | OperationCode/operationcode_frontend | https://api.github.com/repos/OperationCode/operationcode_frontend | closed | Redirect user to intended route after forced login | Priority: Low Type: Feature/Redesign | <!-- Please fill out one of the sections below based on the type of issue you're creating -->
# Feature
## Why is this feature being added?
<!-- What problem is it solving? What value does it add? -->
Current experience:
1) Navigate to www.operationcode.org/scholarships, without being logged in
2) Click on the 'Read More' button for a scholarship, which links to the Scholarship Application Page for that scholarship
3) Since the Application Page for scholarships is an 'Authenticated Route' requiring a user to be logged on, the user is redirected to the Login Page
4) After logging in, the user is redirected to the Profile page, _not_ the Scholarship Application Page they were attempting to navigate to
Let's provides a better user-experience than this. Redirecting the user to the Profile page every time is an unnecessary context switch for a user.
## What should your feature do?
In situations like this (where we redirect a user to the Login page when they're trying to access an Authenticated route), after they log on, let's redirect the user to the page they were originally trying to reach. | 1.0 | Redirect user to intended route after forced login - <!-- Please fill out one of the sections below based on the type of issue you're creating -->
# Feature
## Why is this feature being added?
<!-- What problem is it solving? What value does it add? -->
Current experience:
1) Navigate to www.operationcode.org/scholarships, without being logged in
2) Click on the 'Read More' button for a scholarship, which links to the Scholarship Application Page for that scholarship
3) Since the Application Page for scholarships is an 'Authenticated Route' requiring a user to be logged on, the user is redirected to the Login Page
4) After logging in, the user is redirected to the Profile page, _not_ the Scholarship Application Page they were attempting to navigate to
Let's provides a better user-experience than this. Redirecting the user to the Profile page every time is an unnecessary context switch for a user.
## What should your feature do?
In situations like this (where we redirect a user to the Login page when they're trying to access an Authenticated route), after they log on, let's redirect the user to the page they were originally trying to reach. | design | redirect user to intended route after forced login feature why is this feature being added current experience navigate to without being logged in click on the read more button for a scholarship which links to the scholarship application page for that scholarship since the application page for scholarships is an authenticated route requiring a user to be logged on the user is redirected to the login page after logging in the user is redirected to the profile page not the scholarship application page they were attempting to navigate to let s provides a better user experience than this redirecting the user to the profile page every time is an unnecessary context switch for a user what should your feature do in situations like this where we redirect a user to the login page when they re trying to access an authenticated route after they log on let s redirect the user to the page they were originally trying to reach | 1 |
739,287 | 25,589,439,870 | IssuesEvent | 2022-12-01 11:53:00 | jbx-protocol/juice-interface | https://api.github.com/repos/jbx-protocol/juice-interface | opened | Loader appearing too high on project page | type:bug priority:2 | ## Summary
<img width="1435" alt="Screen Shot 2022-12-01 at 9 52 18 pm" src="https://user-images.githubusercontent.com/96150256/205046074-69298b38-fa5e-464f-8b78-e1c5df5188b2.png">
## Steps to reproduce
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error
## What is the _current_ bug behavior?
## What is the expected _correct_ behavior?
## Relevant logs and/or screenshots
## Environment
- **Device/OS**: [e.g. iOS]
- **Browser:** [e.g. chrome, safari]
- **Hardware wallet**: [e.g. Ledger w/ Metamask]
| 1.0 | Loader appearing too high on project page - ## Summary
<img width="1435" alt="Screen Shot 2022-12-01 at 9 52 18 pm" src="https://user-images.githubusercontent.com/96150256/205046074-69298b38-fa5e-464f-8b78-e1c5df5188b2.png">
## Steps to reproduce
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error
## What is the _current_ bug behavior?
## What is the expected _correct_ behavior?
## Relevant logs and/or screenshots
## Environment
- **Device/OS**: [e.g. iOS]
- **Browser:** [e.g. chrome, safari]
- **Hardware wallet**: [e.g. Ledger w/ Metamask]
| non_design | loader appearing too high on project page summary img width alt screen shot at pm src steps to reproduce go to click on scroll down to see error what is the current bug behavior what is the expected correct behavior relevant logs and or screenshots environment device os browser hardware wallet | 0 |
119,290 | 4,764,067,727 | IssuesEvent | 2016-10-25 15:59:12 | inova-tecnologias/jenova-web | https://api.github.com/repos/inova-tecnologias/jenova-web | closed | bug when logged as Administrator | bug complexity/low priority/P0 | When logged as Administrator profile, the User list don't show correctly users. | 1.0 | bug when logged as Administrator - When logged as Administrator profile, the User list don't show correctly users. | non_design | bug when logged as administrator when logged as administrator profile the user list don t show correctly users | 0 |
108,900 | 13,686,009,840 | IssuesEvent | 2020-09-30 08:03:55 | mdn/yari | https://api.github.com/repos/mdn/yari | closed | Forms | Yari1 design system | Minimalist now contains our core form styles.
- Document examples in Storybook
- Test new form styles in Yari | 1.0 | Forms - Minimalist now contains our core form styles.
- Document examples in Storybook
- Test new form styles in Yari | design | forms minimalist now contains our core form styles document examples in storybook test new form styles in yari | 1 |
100,832 | 12,566,660,160 | IssuesEvent | 2020-06-08 11:37:40 | HumanRightsMeasurementInitiative/hrmi-dataportal | https://api.github.com/repos/HumanRightsMeasurementInitiative/hrmi-dataportal | closed | Develop new landing page | enhancement needs: design | Sometimes referred to "Netflix style" landing page
> the purpose as being to welcome people and give them some ideas of the sorts of things they can do, without requiring them to engage with any actual data. | 1.0 | Develop new landing page - Sometimes referred to "Netflix style" landing page
> the purpose as being to welcome people and give them some ideas of the sorts of things they can do, without requiring them to engage with any actual data. | design | develop new landing page sometimes referred to netflix style landing page the purpose as being to welcome people and give them some ideas of the sorts of things they can do without requiring them to engage with any actual data | 1 |
268,679 | 23,387,813,656 | IssuesEvent | 2022-08-11 15:05:43 | kyma-project/kyma | https://api.github.com/repos/kyma-project/kyma | closed | Improve error logs in Application Connector integration tests | area/application-connector area/tests | **Description**
@kyma-project/framefrog , improve logs from the `pre-main-kyma-integration-k3d-{application-connector-component}` pipelines. Currently, they look kinda gross when they fail. For example, there are multiple dropdowns for a single failure:
<img width="1493" alt="Screenshot 2022-08-03 at 10 01 10" src="https://user-images.githubusercontent.com/32485355/182556179-87f77316-817e-4849-b1d0-ec4d1a91f735.png">
There are also multiple bolded and covered in red lines in the logs below even if they are not important. [Here is an example of such log](https://status.build.kyma-project.io/view/gs/kyma-prow-logs/pr-logs/pull/kyma-project_kyma/14804/pre-main-kyma-integration-k3d-app-gateway/1554052034313850880)
For the successful runs, it doesn't look beautiful either. Look at these bolded errors that mean nothing, as [the pipeline is green](https://status.build.kyma-project.io/view/gs/kyma-prow-logs/pr-logs/pull/kyma-project_kyma/14972/pre-main-kyma-integration-k3d-app-gateway/1554480421897506816):
<img width="1152" alt="Screenshot 2022-08-03 at 10 27 12" src="https://user-images.githubusercontent.com/32485355/182561480-47210135-5bea-4367-85e6-c56246ce9d81.png">
**Reasons**
The log message should be clear. If there are errors, there should be a single dropdown for each one. If there are no errors and the pipeline is green, the logs should not scream with bolded red colored errors everywhere | 1.0 | Improve error logs in Application Connector integration tests - **Description**
@kyma-project/framefrog , improve logs from the `pre-main-kyma-integration-k3d-{application-connector-component}` pipelines. Currently, they look kinda gross when they fail. For example, there are multiple dropdowns for a single failure:
<img width="1493" alt="Screenshot 2022-08-03 at 10 01 10" src="https://user-images.githubusercontent.com/32485355/182556179-87f77316-817e-4849-b1d0-ec4d1a91f735.png">
There are also multiple bolded and covered in red lines in the logs below even if they are not important. [Here is an example of such log](https://status.build.kyma-project.io/view/gs/kyma-prow-logs/pr-logs/pull/kyma-project_kyma/14804/pre-main-kyma-integration-k3d-app-gateway/1554052034313850880)
For the successful runs, it doesn't look beautiful either. Look at these bolded errors that mean nothing, as [the pipeline is green](https://status.build.kyma-project.io/view/gs/kyma-prow-logs/pr-logs/pull/kyma-project_kyma/14972/pre-main-kyma-integration-k3d-app-gateway/1554480421897506816):
<img width="1152" alt="Screenshot 2022-08-03 at 10 27 12" src="https://user-images.githubusercontent.com/32485355/182561480-47210135-5bea-4367-85e6-c56246ce9d81.png">
**Reasons**
The log message should be clear. If there are errors, there should be a single dropdown for each one. If there are no errors and the pipeline is green, the logs should not scream with bolded red colored errors everywhere | non_design | improve error logs in application connector integration tests description kyma project framefrog improve logs from the pre main kyma integration application connector component pipelines currently they look kinda gross when they fail for example there are multiple dropdowns for a single failure img width alt screenshot at src there are also multiple bolded and covered in red lines in the logs below even if they are not important for the successful runs it doesn t look beautiful either look at these bolded errors that mean nothing as img width alt screenshot at src reasons the log message should be clear if there are errors there should be a single dropdown for each one if there are no errors and the pipeline is green the logs should not scream with bolded red colored errors everywhere | 0 |
163,853 | 25,887,865,096 | IssuesEvent | 2022-12-14 15:44:58 | microsoft/pyright | https://api.github.com/repos/microsoft/pyright | closed | Pyright classifies unannotated abstractmethod return as `None` | as designed | **Describe the bug**
It's possible that this is "as designed", but this behavior seems surprising to me:
```
from abc import ABC, abstractmethod
class Foo(ABC):
@abstractmethod
def foo(self):
...
def takes_foo(foo_obj: Foo):
foo_obj.foo() # has type of `None`
```
It looks like the same inference rules applied to normal methods are applied to abstract methods, so that the lack of a return statement in the abstract method causes pyright to infer a type of `None`. But since abstract methods can never have a return statement in the body, this is an unjustified inference-- it seems more sensible to have an `Unknown` return type for an unannotated abstract method. | 1.0 | Pyright classifies unannotated abstractmethod return as `None` - **Describe the bug**
It's possible that this is "as designed", but this behavior seems surprising to me:
```
from abc import ABC, abstractmethod
class Foo(ABC):
@abstractmethod
def foo(self):
...
def takes_foo(foo_obj: Foo):
foo_obj.foo() # has type of `None`
```
It looks like the same inference rules applied to normal methods are applied to abstract methods, so that the lack of a return statement in the abstract method causes pyright to infer a type of `None`. But since abstract methods can never have a return statement in the body, this is an unjustified inference-- it seems more sensible to have an `Unknown` return type for an unannotated abstract method. | design | pyright classifies unannotated abstractmethod return as none describe the bug it s possible that this is as designed but this behavior seems surprising to me from abc import abc abstractmethod class foo abc abstractmethod def foo self def takes foo foo obj foo foo obj foo has type of none it looks like the same inference rules applied to normal methods are applied to abstract methods so that the lack of a return statement in the abstract method causes pyright to infer a type of none but since abstract methods can never have a return statement in the body this is an unjustified inference it seems more sensible to have an unknown return type for an unannotated abstract method | 1 |
177,827 | 29,170,694,802 | IssuesEvent | 2023-05-19 01:18:30 | wpumacay/renderer | https://api.github.com/repos/wpumacay/renderer | closed | Camera Controls Objects (camera_control_t) | component: python priority: high type: design type: documentation type: feature component: engine objects | <!-- TODO(wilbert) -->
- [x] Orbit controls
- [ ] Fps controls
- [ ] Mixes|Hibrid|Editor controls | 1.0 | Camera Controls Objects (camera_control_t) - <!-- TODO(wilbert) -->
- [x] Orbit controls
- [ ] Fps controls
- [ ] Mixes|Hibrid|Editor controls | design | camera controls objects camera control t orbit controls fps controls mixes hibrid editor controls | 1 |
43,203 | 5,583,791,871 | IssuesEvent | 2017-03-29 01:54:46 | ParabolInc/action | https://api.github.com/repos/ParabolInc/action | opened | Label enhancement implemented | designing enhancement help wanted idea | ## Enhancement
When a team is working on projects that span across common work themes (epics, recurring, etc.), team members want a smart labeling system so that they can tag and filter projects.
Spec:
- [ ] Users can type labels anywhere in the content, beginning with a hashtag
- [ ] An inline autocomplete (and automagical, I might say) menu appears (triggered by the keystroke of a hashtag) that suggests existing labels (to reduce duplicates)
- [ ] Users can click labels to filter projects by that label (which updates the smart search bar and/or existing filter state [TBD, link here])
- [ ] Alternatively, users can filter by labels using the smart search bar and/or some other filter control [TBD, link here]
Candidates for superpowers:
- [ ] Consider the ability to enable/disable label superpowers at the team settings level
- [ ] #private makes a project only visible to the owner (consider styling the card with “private” styles [use legacy Action card colors? use a cooler incognito theme?]
- [ ] #recurring gets moved to Future when moved to Done during a meeting (instead of archiving)
- [ ] #priority each team member can mark one card as their priority (signals to other team members what their #1 project is at the moment)
- [ ] +#123 associates the project with another project by visible ID
- [ ] >#123 references a project blocked by the *this* project
- [ ] <#123 references a project that is blocking *this* project
Considerations for integrations:
- [ ] GitHub, when a hashtag appears before an issue number on GitHub, it should form a link. In our dashboard should we link to GitHub or to an imported, synced copy of the issue in our own software?
**Estimated effort**: 23 points ([see CONTRIBUTING.md](https://github.com/ParabolInc/action/blob/master/CONTRIBUTING.md#points-and-sizes))
| 1.0 | Label enhancement implemented - ## Enhancement
When a team is working on projects that span across common work themes (epics, recurring, etc.), team members want a smart labeling system so that they can tag and filter projects.
Spec:
- [ ] Users can type labels anywhere in the content, beginning with a hashtag
- [ ] An inline autocomplete (and automagical, I might say) menu appears (triggered by the keystroke of a hashtag) that suggests existing labels (to reduce duplicates)
- [ ] Users can click labels to filter projects by that label (which updates the smart search bar and/or existing filter state [TBD, link here])
- [ ] Alternatively, users can filter by labels using the smart search bar and/or some other filter control [TBD, link here]
Candidates for superpowers:
- [ ] Consider the ability to enable/disable label superpowers at the team settings level
- [ ] #private makes a project only visible to the owner (consider styling the card with “private” styles [use legacy Action card colors? use a cooler incognito theme?]
- [ ] #recurring gets moved to Future when moved to Done during a meeting (instead of archiving)
- [ ] #priority each team member can mark one card as their priority (signals to other team members what their #1 project is at the moment)
- [ ] +#123 associates the project with another project by visible ID
- [ ] >#123 references a project blocked by the *this* project
- [ ] <#123 references a project that is blocking *this* project
Considerations for integrations:
- [ ] GitHub, when a hashtag appears before an issue number on GitHub, it should form a link. In our dashboard should we link to GitHub or to an imported, synced copy of the issue in our own software?
**Estimated effort**: 23 points ([see CONTRIBUTING.md](https://github.com/ParabolInc/action/blob/master/CONTRIBUTING.md#points-and-sizes))
| design | label enhancement implemented enhancement when a team is working on projects that span across common work themes epics recurring etc team members want a smart labeling system so that they can tag and filter projects spec users can type labels anywhere in the content beginning with a hashtag an inline autocomplete and automagical i might say menu appears triggered by the keystroke of a hashtag that suggests existing labels to reduce duplicates users can click labels to filter projects by that label which updates the smart search bar and or existing filter state alternatively users can filter by labels using the smart search bar and or some other filter control candidates for superpowers consider the ability to enable disable label superpowers at the team settings level private makes a project only visible to the owner consider styling the card with “private” styles recurring gets moved to future when moved to done during a meeting instead of archiving priority each team member can mark one card as their priority signals to other team members what their project is at the moment associates the project with another project by visible id references a project blocked by the this project references a project that is blocking this project considerations for integrations github when a hashtag appears before an issue number on github it should form a link in our dashboard should we link to github or to an imported synced copy of the issue in our own software estimated effort points | 1 |
74,317 | 25,065,416,299 | IssuesEvent | 2022-11-07 07:51:31 | hazelcast/hazelcast-nodejs-client | https://api.github.com/repos/hazelcast/hazelcast-nodejs-client | closed | While config Inputs are invalid, error message is not enough [API-1490] | Type: Defect to-jira | While configuring the client, if the inputs are invalid such as (use this as it is, do not change anything)
`{
network: {
hazelcastCloud: {
discoveryToken: 'YOUR_DISCOVERY_TOKEN'
}
},
clusterName: 'YOUR_CLUSTER_NAME'
}`
, returned error message is
`[DefaultLogger] INFO at LifecycleService: HazelcastClient is STARTING
[DefaultLogger] INFO at LifecycleService: HazelcastClient is STARTED
/PATH-TO-PROJECT/node_modules/hazelcast-client/lib/discovery/HazelcastCloudDiscovery.js:75
for (const value of jsonValue) {
^
TypeError: jsonValue is not iterable
at Function.parseResponse (/PATH-TO-PROJECT/node_modules/hazelcast-client/lib/discovery/HazelcastCloudDiscovery.js:75:29)
at IncomingMessage.<anonymous> (/PATH-TO-PROJECT/node_modules/hazelcast-client/lib/discovery/HazelcastCloudDiscovery.js:61:58)
at IncomingMessage.emit (node:events:539:35)
at endReadableNT (node:internal/streams/readable:1345:12)
at processTicksAndRejections (node:internal/process/task_queues:83:21)`
however there should be a better error message. | 1.0 | While config Inputs are invalid, error message is not enough [API-1490] - While configuring the client, if the inputs are invalid such as (use this as it is, do not change anything)
`{
network: {
hazelcastCloud: {
discoveryToken: 'YOUR_DISCOVERY_TOKEN'
}
},
clusterName: 'YOUR_CLUSTER_NAME'
}`
, returned error message is
`[DefaultLogger] INFO at LifecycleService: HazelcastClient is STARTING
[DefaultLogger] INFO at LifecycleService: HazelcastClient is STARTED
/PATH-TO-PROJECT/node_modules/hazelcast-client/lib/discovery/HazelcastCloudDiscovery.js:75
for (const value of jsonValue) {
^
TypeError: jsonValue is not iterable
at Function.parseResponse (/PATH-TO-PROJECT/node_modules/hazelcast-client/lib/discovery/HazelcastCloudDiscovery.js:75:29)
at IncomingMessage.<anonymous> (/PATH-TO-PROJECT/node_modules/hazelcast-client/lib/discovery/HazelcastCloudDiscovery.js:61:58)
at IncomingMessage.emit (node:events:539:35)
at endReadableNT (node:internal/streams/readable:1345:12)
at processTicksAndRejections (node:internal/process/task_queues:83:21)`
however there should be a better error message. | non_design | while config inputs are invalid error message is not enough while configuring the client if the inputs are invalid such as use this as it is do not change anything network hazelcastcloud discoverytoken your discovery token clustername your cluster name returned error message is info at lifecycleservice hazelcastclient is starting info at lifecycleservice hazelcastclient is started path to project node modules hazelcast client lib discovery hazelcastclouddiscovery js for const value of jsonvalue typeerror jsonvalue is not iterable at function parseresponse path to project node modules hazelcast client lib discovery hazelcastclouddiscovery js at incomingmessage path to project node modules hazelcast client lib discovery hazelcastclouddiscovery js at incomingmessage emit node events at endreadablent node internal streams readable at processticksandrejections node internal process task queues however there should be a better error message | 0 |
181,775 | 30,740,554,038 | IssuesEvent | 2023-07-28 11:06:48 | hlxsites/mammotome | https://api.github.com/repos/hlxsites/mammotome | closed | General Refresh Styles | enhancement refresh-design | Add general refresh styles, scoped to the `refresh` body class (set via Theme page metadata property) | 1.0 | General Refresh Styles - Add general refresh styles, scoped to the `refresh` body class (set via Theme page metadata property) | design | general refresh styles add general refresh styles scoped to the refresh body class set via theme page metadata property | 1 |
711,594 | 24,468,970,471 | IssuesEvent | 2022-10-07 17:45:00 | project-chip/zap | https://api.github.com/repos/project-chip/zap | closed | Cleanup zap/repo/src-electron/generator/matter/chip-tool | high priority MatterZapCleanup | The goal is to eventually cleanup the matter specific zap code to not have any state for eg in ClustersHelper.js
During this cleanup we want to do the following:
- Go through the matter directory in this issue. See if these helpers can have code pushed to the backend sql queries.
- See if the helpers can use any of the existing helper logic and can remove code redundancy
- Add unit tests for each of the helpers listed
- Make sure to have a CHIP/Zigbee repo branch that points to your changes and passes the CI on both places
- Also if you can fix anything new apart from what is listed then fix those issues as well.
| 1.0 | Cleanup zap/repo/src-electron/generator/matter/chip-tool - The goal is to eventually cleanup the matter specific zap code to not have any state for eg in ClustersHelper.js
During this cleanup we want to do the following:
- Go through the matter directory in this issue. See if these helpers can have code pushed to the backend sql queries.
- See if the helpers can use any of the existing helper logic and can remove code redundancy
- Add unit tests for each of the helpers listed
- Make sure to have a CHIP/Zigbee repo branch that points to your changes and passes the CI on both places
- Also if you can fix anything new apart from what is listed then fix those issues as well.
| non_design | cleanup zap repo src electron generator matter chip tool the goal is to eventually cleanup the matter specific zap code to not have any state for eg in clustershelper js during this cleanup we want to do the following go through the matter directory in this issue see if these helpers can have code pushed to the backend sql queries see if the helpers can use any of the existing helper logic and can remove code redundancy add unit tests for each of the helpers listed make sure to have a chip zigbee repo branch that points to your changes and passes the ci on both places also if you can fix anything new apart from what is listed then fix those issues as well | 0 |
49,540 | 6,223,461,141 | IssuesEvent | 2017-07-10 12:00:01 | pandas-dev/pandas | https://api.github.com/repos/pandas-dev/pandas | closed | Assignment by Attribute has Odd Behavior | API Design Indexing | When assigning to a column in a DataFrame, If I assign an existing column, the assignment works:
```
In [36]: df = pd.DataFrame({'a':[1,2,12], 'b':['a','b','a']})
In [37]: df.b = df.a
In [38]: print df
a b
0 1 1
1 2 2
2 12 12
[3 rows x 2 columns]
```
but assigning to a new column fails silently:
```
In [40]:df = pd.DataFrame({'a':[1,2,12], 'b':['a','b','a']})
In [41]:df.c = df.a
In [42]:print df
a b
0 1 a
1 2 b
2 12 a
[3 rows x 2 columns]
```
| 1.0 | Assignment by Attribute has Odd Behavior - When assigning to a column in a DataFrame, If I assign an existing column, the assignment works:
```
In [36]: df = pd.DataFrame({'a':[1,2,12], 'b':['a','b','a']})
In [37]: df.b = df.a
In [38]: print df
a b
0 1 1
1 2 2
2 12 12
[3 rows x 2 columns]
```
but assigning to a new column fails silently:
```
In [40]:df = pd.DataFrame({'a':[1,2,12], 'b':['a','b','a']})
In [41]:df.c = df.a
In [42]:print df
a b
0 1 a
1 2 b
2 12 a
[3 rows x 2 columns]
```
| design | assignment by attribute has odd behavior when assigning to a column in a dataframe if i assign an existing column the assignment works in df pd dataframe a b in df b df a in print df a b but assigning to a new column fails silently in df pd dataframe a b in df c df a in print df a b a b a | 1 |
115,164 | 14,699,687,813 | IssuesEvent | 2021-01-04 08:59:51 | filecoin-project/venus | https://api.github.com/repos/filecoin-project/venus | closed | Graphsync fetcher inter-request parallelism | needs-design :scroll: request-for-input | ### Description
It may make sense to request multiple chain heads in parallel instead of blocking on a single mutex in the syncer's `HandleNewTipSet` function.
For example if one block is only served by a peer that conveniently disconnects during fetching that peer can cause the graphsync system to retry for the entire `requestTimeout`, preventing the fetching and processing of other blocks.
### Acceptance criteria
- We have good reason to believe this will improve performance or DOS resistance
- We can safely fetch multiple chains in parallel
### Risks + pitfalls
- This will use more resources and so we should make sure it is worth the cost
- If this is done incorrectly it will be wasteful. For example we should never be fetching `N` fetcher requests for the same head at once (we may want to have redundant fetches -- see #3372 -- but those should be managed carefully on a per request basis, not allowed to blowup based on repeated network messages for the same head)
- Correctly determining that two chains do not intersect before fetch is actually not something we can do right now. We'd need more information (i.e. (cid, height) for every X blocks) from the hello protocol or peer tracker before this makes sense to do.
- This is only for parallelizing fetches, not block processing which presents other concerns
### Where to begin
Discussion with @frrist @anorth @hannahhoward | 1.0 | Graphsync fetcher inter-request parallelism - ### Description
It may make sense to request multiple chain heads in parallel instead of blocking on a single mutex in the syncer's `HandleNewTipSet` function.
For example if one block is only served by a peer that conveniently disconnects during fetching that peer can cause the graphsync system to retry for the entire `requestTimeout`, preventing the fetching and processing of other blocks.
### Acceptance criteria
- We have good reason to believe this will improve performance or DOS resistance
- We can safely fetch multiple chains in parallel
### Risks + pitfalls
- This will use more resources and so we should make sure it is worth the cost
- If this is done incorrectly it will be wasteful. For example we should never be fetching `N` fetcher requests for the same head at once (we may want to have redundant fetches -- see #3372 -- but those should be managed carefully on a per request basis, not allowed to blowup based on repeated network messages for the same head)
- Correctly determining that two chains do not intersect before fetch is actually not something we can do right now. We'd need more information (i.e. (cid, height) for every X blocks) from the hello protocol or peer tracker before this makes sense to do.
- This is only for parallelizing fetches, not block processing which presents other concerns
### Where to begin
Discussion with @frrist @anorth @hannahhoward | design | graphsync fetcher inter request parallelism description it may make sense to request multiple chain heads in parallel instead of blocking on a single mutex in the syncer s handlenewtipset function for example if one block is only served by a peer that conveniently disconnects during fetching that peer can cause the graphsync system to retry for the entire requesttimeout preventing the fetching and processing of other blocks acceptance criteria we have good reason to believe this will improve performance or dos resistance we can safely fetch multiple chains in parallel risks pitfalls this will use more resources and so we should make sure it is worth the cost if this is done incorrectly it will be wasteful for example we should never be fetching n fetcher requests for the same head at once we may want to have redundant fetches see but those should be managed carefully on a per request basis not allowed to blowup based on repeated network messages for the same head correctly determining that two chains do not intersect before fetch is actually not something we can do right now we d need more information i e cid height for every x blocks from the hello protocol or peer tracker before this makes sense to do this is only for parallelizing fetches not block processing which presents other concerns where to begin discussion with frrist anorth hannahhoward | 1 |
159,548 | 25,015,085,951 | IssuesEvent | 2022-11-03 18:05:45 | microsoft/TypeScript | https://api.github.com/repos/microsoft/TypeScript | closed | Enums does not support literal typing with computed values | Design Limitation Fix Available | <!-- 🚨 STOP 🚨 𝗦𝗧𝗢𝗣 🚨 𝑺𝑻𝑶𝑷 🚨
Half of all issues filed here are duplicates, answered in the FAQ, or not appropriate for the bug tracker. Even if you think you've found a *bug*, please read the FAQ first, especially the Common "Bugs" That Aren't Bugs section!
Please help us by doing the following steps before logging an issue:
* Search: https://github.com/Microsoft/TypeScript/search?type=Issues
* Read the FAQ: https://github.com/Microsoft/TypeScript/wiki/FAQ
Please fill in the *entire* template below.
-->
<!-- Please try to reproduce the issue with `typescript@next`. It may have already been fixed. -->
**TypeScript Version:** 3.2.0-dev.201xxxxx
<!-- Search terms you tried before logging this (so others can find this issue more easily) -->
**Search Terms:**
- enum flag
- enum computed literal typing
**Code**
```ts
enum AnimalFlags {
None = 0,
HasClaws = 1 << 0,
CanFly = 1 << 1,
EatsFish = 1 << 2,
Endangered = 1 << 3,
EndangeredFlyingClawedFishEating = HasClaws | CanFly | EatsFish | Endangered,
}
enum RegularEnum {
None,
HasPowers,
}
const a = AnimalFlags.EatsFish;
const b: AnimalFlags.EndangeredFlyingClawedFishEating = AnimalFlags.EndangeredFlyingClawedFishEating;
const c = RegularEnum.HasPowers;
```
**Expected behavior:**
`a` Should have type of `AnimalFlags.EatsFish`
`b` Should not throw. Should allow the assignment of `AnimalFlags.EndangeredFlyingClawedFishEating` as type.
I would expect a computed Enum to behave as a regular enum, in this case, `c` has type `RegularEnum.HasPowers`
**Actual behavior:**
`a` is typed as `AnimalFlags`.
`const b: AnimalFlags.EndangeredFlyingClawedFishEating` is throwing `Enum type 'AnimalFlags' has members with initializers that are not literals.`
`b` should be allowed to be typed as `AnimalFlags.EndangeredFlyingClawedFishEating`.
**Playground Link:** <!-- A link to a TypeScript Playground "Share" link which demonstrates this behavior -->
[Link](http://www.typescriptlang.org/play/#src=enum%20AnimalFlags%20%7B%0D%0A%20%20%20%20None%20%20%20%20%20%20%20%20%20%20%20%3D%200%2C%0D%0A%20%20%20%20HasClaws%20%20%20%20%20%20%20%3D%201%20%3C%3C%200%2C%0D%0A%20%20%20%20CanFly%20%20%20%20%20%20%20%20%20%3D%201%20%3C%3C%201%2C%0D%0A%20%20%20%20EatsFish%20%20%20%20%20%20%20%3D%201%20%3C%3C%202%2C%0D%0A%20%20%20%20Endangered%20%20%20%20%20%3D%201%20%3C%3C%203%2C%0D%0A%0D%0A%20%20%20%20EndangeredFlyingClawedFishEating%20%3D%20HasClaws%20%7C%20CanFly%20%7C%20EatsFish%20%7C%20Endangered%2C%0D%0A%7D%0D%0A%0D%0Aenum%20RegularEnum%20%7B%0D%0A%20%20%20%20None%2C%0D%0A%20%20%20%20HasPowers%2C%0D%0A%7D%0D%0A%0D%0A%0D%0Aconst%20a%20%3D%20AnimalFlags.EatsFish%3B%0D%0Aconst%20b%3A%20AnimalFlags.EndangeredFlyingClawedFishEating%20%3D%20AnimalFlags.EndangeredFlyingClawedFishEating%3B%0D%0Aconst%20c%20%3D%20RegularEnum.HasPowers%3B)
**Related Issues:** <!-- Did you find other bugs that looked similar? -->
I think is the same that one reported last year #18393. It was closed as a Design Limitation, but since there has been some big changes in Typescript maybe this would be worth to be reviewed again. | 1.0 | Enums does not support literal typing with computed values - <!-- 🚨 STOP 🚨 𝗦𝗧𝗢𝗣 🚨 𝑺𝑻𝑶𝑷 🚨
Half of all issues filed here are duplicates, answered in the FAQ, or not appropriate for the bug tracker. Even if you think you've found a *bug*, please read the FAQ first, especially the Common "Bugs" That Aren't Bugs section!
Please help us by doing the following steps before logging an issue:
* Search: https://github.com/Microsoft/TypeScript/search?type=Issues
* Read the FAQ: https://github.com/Microsoft/TypeScript/wiki/FAQ
Please fill in the *entire* template below.
-->
<!-- Please try to reproduce the issue with `typescript@next`. It may have already been fixed. -->
**TypeScript Version:** 3.2.0-dev.201xxxxx
<!-- Search terms you tried before logging this (so others can find this issue more easily) -->
**Search Terms:**
- enum flag
- enum computed literal typing
**Code**
```ts
enum AnimalFlags {
None = 0,
HasClaws = 1 << 0,
CanFly = 1 << 1,
EatsFish = 1 << 2,
Endangered = 1 << 3,
EndangeredFlyingClawedFishEating = HasClaws | CanFly | EatsFish | Endangered,
}
enum RegularEnum {
None,
HasPowers,
}
const a = AnimalFlags.EatsFish;
const b: AnimalFlags.EndangeredFlyingClawedFishEating = AnimalFlags.EndangeredFlyingClawedFishEating;
const c = RegularEnum.HasPowers;
```
**Expected behavior:**
`a` Should have type of `AnimalFlags.EatsFish`
`b` Should not throw. Should allow the assignment of `AnimalFlags.EndangeredFlyingClawedFishEating` as type.
I would expect a computed Enum to behave as a regular enum, in this case, `c` has type `RegularEnum.HasPowers`
**Actual behavior:**
`a` is typed as `AnimalFlags`.
`const b: AnimalFlags.EndangeredFlyingClawedFishEating` is throwing `Enum type 'AnimalFlags' has members with initializers that are not literals.`
`b` should be allowed to be typed as `AnimalFlags.EndangeredFlyingClawedFishEating`.
**Playground Link:** <!-- A link to a TypeScript Playground "Share" link which demonstrates this behavior -->
[Link](http://www.typescriptlang.org/play/#src=enum%20AnimalFlags%20%7B%0D%0A%20%20%20%20None%20%20%20%20%20%20%20%20%20%20%20%3D%200%2C%0D%0A%20%20%20%20HasClaws%20%20%20%20%20%20%20%3D%201%20%3C%3C%200%2C%0D%0A%20%20%20%20CanFly%20%20%20%20%20%20%20%20%20%3D%201%20%3C%3C%201%2C%0D%0A%20%20%20%20EatsFish%20%20%20%20%20%20%20%3D%201%20%3C%3C%202%2C%0D%0A%20%20%20%20Endangered%20%20%20%20%20%3D%201%20%3C%3C%203%2C%0D%0A%0D%0A%20%20%20%20EndangeredFlyingClawedFishEating%20%3D%20HasClaws%20%7C%20CanFly%20%7C%20EatsFish%20%7C%20Endangered%2C%0D%0A%7D%0D%0A%0D%0Aenum%20RegularEnum%20%7B%0D%0A%20%20%20%20None%2C%0D%0A%20%20%20%20HasPowers%2C%0D%0A%7D%0D%0A%0D%0A%0D%0Aconst%20a%20%3D%20AnimalFlags.EatsFish%3B%0D%0Aconst%20b%3A%20AnimalFlags.EndangeredFlyingClawedFishEating%20%3D%20AnimalFlags.EndangeredFlyingClawedFishEating%3B%0D%0Aconst%20c%20%3D%20RegularEnum.HasPowers%3B)
**Related Issues:** <!-- Did you find other bugs that looked similar? -->
I think is the same that one reported last year #18393. It was closed as a Design Limitation, but since there has been some big changes in Typescript maybe this would be worth to be reviewed again. | design | enums does not support literal typing with computed values 🚨 stop 🚨 𝗦𝗧𝗢𝗣 🚨 𝑺𝑻𝑶𝑷 🚨 half of all issues filed here are duplicates answered in the faq or not appropriate for the bug tracker even if you think you ve found a bug please read the faq first especially the common bugs that aren t bugs section please help us by doing the following steps before logging an issue search read the faq please fill in the entire template below typescript version dev search terms enum flag enum computed literal typing code ts enum animalflags none hasclaws canfly eatsfish endangered endangeredflyingclawedfisheating hasclaws canfly eatsfish endangered enum regularenum none haspowers const a animalflags eatsfish const b animalflags endangeredflyingclawedfisheating animalflags endangeredflyingclawedfisheating const c regularenum haspowers expected behavior a should have type of animalflags eatsfish b should not throw should allow the assignment of animalflags endangeredflyingclawedfisheating as type i would expect a computed enum to behave as a regular enum in this case c has type regularenum haspowers actual behavior a is typed as animalflags const b animalflags endangeredflyingclawedfisheating is throwing enum type animalflags has members with initializers that are not literals b should be allowed to be typed as animalflags endangeredflyingclawedfisheating playground link related issues i think is the same that one reported last year it was closed as a design limitation but since there has been some big changes in typescript maybe this would be worth to be reviewed again | 1 |
147,381 | 23,209,631,568 | IssuesEvent | 2022-08-02 09:00:37 | appsmithorg/appsmith | https://api.github.com/repos/appsmithorg/appsmith | closed | [Task]: Remove unused workflows in design-system repository | Design System Pod Task | ### Is there an existing issue for this?
- [X] I have searched the existing issues
### SubTasks
- Add sprint assignment in checklist | 1.0 | [Task]: Remove unused workflows in design-system repository - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### SubTasks
- Add sprint assignment in checklist | design | remove unused workflows in design system repository is there an existing issue for this i have searched the existing issues subtasks add sprint assignment in checklist | 1 |
399,321 | 27,236,481,806 | IssuesEvent | 2023-02-21 16:41:05 | microsoft/vscode-vsce | https://api.github.com/repos/microsoft/vscode-vsce | closed | Unmentioned global yarn requirement for tests | documentation | I was playing around with the codebase and ran into some failures after executing the tests because I do not have [`yarn`](https://www.npmjs.com/package/yarn) on my system (console output below)
AFAICT this is because there's a handful of tests that have an undocumented dependency on yarn being installed globally. I imagine there's a few different ways to address this, but IMO it'd be best to either skip those few tests when `yarn` is unavailable or to at least mention the requirement in the documentation.
FWIW I think the former would be better since it's got the lower barrier of entry for contributors between the two, however, I'll send PRs to cover both approaches in case folks feel differently.
Here's the output I received from cloning the repo, running `npm i`, and then running `npm test`:
```console
147 passing (7s)
4 failing
1) collect
should honor dependencyEntryPoints:
Error: Command failed: yarn list --prod --json
/bin/sh: 1: yarn: not found
at ChildProcess.exithandler (node:child_process:399:12)
at ChildProcess.emit (node:events:526:28)
at ChildProcess.emit (node:domain:475:12)
at maybeClose (node:internal/child_process:1092:16)
at Socket.<anonymous> (node:internal/child_process:451:11)
at Socket.emit (node:events:526:28)
at Socket.emit (node:domain:475:12)
at Pipe.<anonymous> (node:net:687:12)
2) collect
should detect yarn:
Error: Command failed: yarn list --prod --json
/bin/sh: 1: yarn: not found
at ChildProcess.exithandler (node:child_process:399:12)
at ChildProcess.emit (node:events:526:28)
at ChildProcess.emit (node:domain:475:12)
at maybeClose (node:internal/child_process:1092:16)
at Socket.<anonymous> (node:internal/child_process:451:11)
at Socket.emit (node:events:526:28)
at Socket.emit (node:domain:475:12)
at Pipe.<anonymous> (node:net:687:12)
3) collect
should include all node_modules when dependencyEntryPoints is not defined:
Error: Command failed: yarn list --prod --json
/bin/sh: 1: yarn: not found
at ChildProcess.exithandler (node:child_process:399:12)
at ChildProcess.emit (node:events:526:28)
at ChildProcess.emit (node:domain:475:12)
at maybeClose (node:internal/child_process:1092:16)
at Socket.<anonymous> (node:internal/child_process:451:11)
at Socket.emit (node:events:526:28)
at Socket.emit (node:domain:475:12)
at Pipe.<anonymous> (node:net:687:12)
4) collect
should skip all node_modules when dependencyEntryPoints is []:
Error: Command failed: yarn list --prod --json
/bin/sh: 1: yarn: not found
at ChildProcess.exithandler (node:child_process:399:12)
at ChildProcess.emit (node:events:526:28)
at ChildProcess.emit (node:domain:475:12)
at maybeClose (node:internal/child_process:1092:16)
at Socket.<anonymous> (node:internal/child_process:451:11)
at Socket.emit (node:events:526:28)
at Socket.emit (node:domain:475:12)
at Pipe.<anonymous> (node:net:687:12)
``` | 1.0 | Unmentioned global yarn requirement for tests - I was playing around with the codebase and ran into some failures after executing the tests because I do not have [`yarn`](https://www.npmjs.com/package/yarn) on my system (console output below)
AFAICT this is because there's a handful of tests that have an undocumented dependency on yarn being installed globally. I imagine there's a few different ways to address this, but IMO it'd be best to either skip those few tests when `yarn` is unavailable or to at least mention the requirement in the documentation.
FWIW I think the former would be better since it's got the lower barrier of entry for contributors between the two, however, I'll send PRs to cover both approaches in case folks feel differently.
Here's the output I received from cloning the repo, running `npm i`, and then running `npm test`:
```console
147 passing (7s)
4 failing
1) collect
should honor dependencyEntryPoints:
Error: Command failed: yarn list --prod --json
/bin/sh: 1: yarn: not found
at ChildProcess.exithandler (node:child_process:399:12)
at ChildProcess.emit (node:events:526:28)
at ChildProcess.emit (node:domain:475:12)
at maybeClose (node:internal/child_process:1092:16)
at Socket.<anonymous> (node:internal/child_process:451:11)
at Socket.emit (node:events:526:28)
at Socket.emit (node:domain:475:12)
at Pipe.<anonymous> (node:net:687:12)
2) collect
should detect yarn:
Error: Command failed: yarn list --prod --json
/bin/sh: 1: yarn: not found
at ChildProcess.exithandler (node:child_process:399:12)
at ChildProcess.emit (node:events:526:28)
at ChildProcess.emit (node:domain:475:12)
at maybeClose (node:internal/child_process:1092:16)
at Socket.<anonymous> (node:internal/child_process:451:11)
at Socket.emit (node:events:526:28)
at Socket.emit (node:domain:475:12)
at Pipe.<anonymous> (node:net:687:12)
3) collect
should include all node_modules when dependencyEntryPoints is not defined:
Error: Command failed: yarn list --prod --json
/bin/sh: 1: yarn: not found
at ChildProcess.exithandler (node:child_process:399:12)
at ChildProcess.emit (node:events:526:28)
at ChildProcess.emit (node:domain:475:12)
at maybeClose (node:internal/child_process:1092:16)
at Socket.<anonymous> (node:internal/child_process:451:11)
at Socket.emit (node:events:526:28)
at Socket.emit (node:domain:475:12)
at Pipe.<anonymous> (node:net:687:12)
4) collect
should skip all node_modules when dependencyEntryPoints is []:
Error: Command failed: yarn list --prod --json
/bin/sh: 1: yarn: not found
at ChildProcess.exithandler (node:child_process:399:12)
at ChildProcess.emit (node:events:526:28)
at ChildProcess.emit (node:domain:475:12)
at maybeClose (node:internal/child_process:1092:16)
at Socket.<anonymous> (node:internal/child_process:451:11)
at Socket.emit (node:events:526:28)
at Socket.emit (node:domain:475:12)
at Pipe.<anonymous> (node:net:687:12)
``` | non_design | unmentioned global yarn requirement for tests i was playing around with the codebase and ran into some failures after executing the tests because i do not have on my system console output below afaict this is because there s a handful of tests that have an undocumented dependency on yarn being installed globally i imagine there s a few different ways to address this but imo it d be best to either skip those few tests when yarn is unavailable or to at least mention the requirement in the documentation fwiw i think the former would be better since it s got the lower barrier of entry for contributors between the two however i ll send prs to cover both approaches in case folks feel differently here s the output i received from cloning the repo running npm i and then running npm test console passing failing collect should honor dependencyentrypoints error command failed yarn list prod json bin sh yarn not found at childprocess exithandler node child process at childprocess emit node events at childprocess emit node domain at maybeclose node internal child process at socket node internal child process at socket emit node events at socket emit node domain at pipe node net collect should detect yarn error command failed yarn list prod json bin sh yarn not found at childprocess exithandler node child process at childprocess emit node events at childprocess emit node domain at maybeclose node internal child process at socket node internal child process at socket emit node events at socket emit node domain at pipe node net collect should include all node modules when dependencyentrypoints is not defined error command failed yarn list prod json bin sh yarn not found at childprocess exithandler node child process at childprocess emit node events at childprocess emit node domain at maybeclose node internal child process at socket node internal child process at socket emit node events at socket emit node domain at pipe node net collect should skip all node modules when dependencyentrypoints is error command failed yarn list prod json bin sh yarn not found at childprocess exithandler node child process at childprocess emit node events at childprocess emit node domain at maybeclose node internal child process at socket node internal child process at socket emit node events at socket emit node domain at pipe node net | 0 |
112,467 | 14,259,373,227 | IssuesEvent | 2020-11-20 08:09:55 | nuvla/ui | https://api.github.com/repos/nuvla/ui | closed | Get rid of cards inside the detail pages | UI Redesign | move/distribute the info someplace else in the same page
(start with the NB page as a prototype) | 1.0 | Get rid of cards inside the detail pages - move/distribute the info someplace else in the same page
(start with the NB page as a prototype) | design | get rid of cards inside the detail pages move distribute the info someplace else in the same page start with the nb page as a prototype | 1 |
107,706 | 13,503,651,480 | IssuesEvent | 2020-09-13 14:30:52 | rubyforgood/casa | https://api.github.com/repos/rubyforgood/casa | closed | Make edit profile accessible by dropdown menu in All CASA Admin dashboard | :cityscape: Multitenancy :globe_with_meridians: All CASA Admin :paintbrush: Design Good First Issue Help Wanted Priority: High Ruby For Good 🎃 Fall 2020 | Part of epic #527
**What type of user is this for? [volunteer/admin/supervisor/all or All CASA Admin]**
All CASA Admin
**Where does/should this occur?**
In the All CASA Admin dashboard (dependent on #628)
**Description**
All CASA Admin needs an entry point to their Edit Profile page. It should be accessible by clicking on their email in the upper right hand corner of their user dashboard. When they click, "Edit Profile" should appear as the only option in a drop down menu.
Log in as any other user to see how this should look. <a href="https://github.com/rubyforgood/casa/blob/master/db/seeds.rb>Login instructions here.</a>
**Screenshots**
It should look like this:
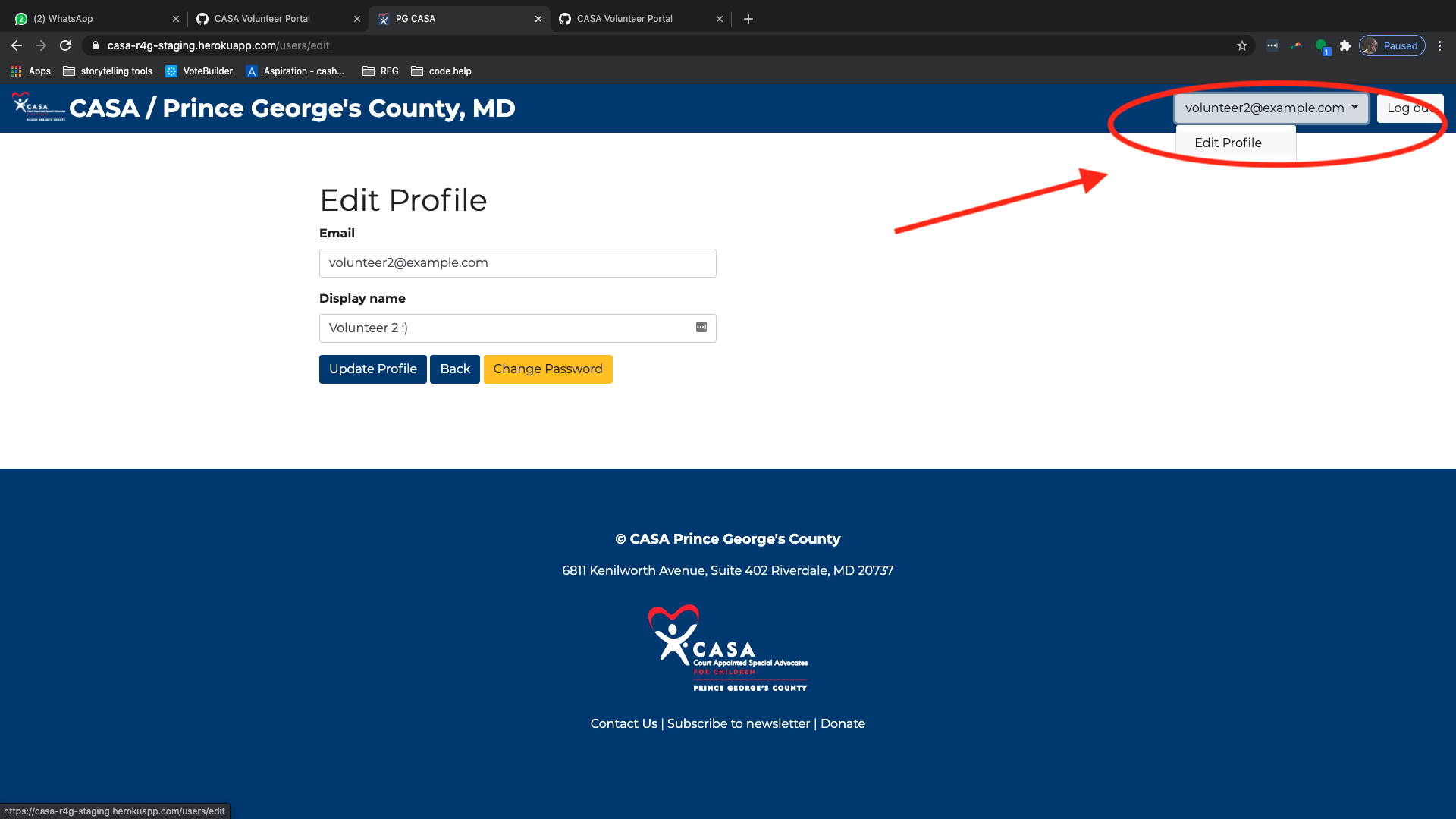
Relates to issues: #627, #628, #630 | 1.0 | Make edit profile accessible by dropdown menu in All CASA Admin dashboard - Part of epic #527
**What type of user is this for? [volunteer/admin/supervisor/all or All CASA Admin]**
All CASA Admin
**Where does/should this occur?**
In the All CASA Admin dashboard (dependent on #628)
**Description**
All CASA Admin needs an entry point to their Edit Profile page. It should be accessible by clicking on their email in the upper right hand corner of their user dashboard. When they click, "Edit Profile" should appear as the only option in a drop down menu.
Log in as any other user to see how this should look. <a href="https://github.com/rubyforgood/casa/blob/master/db/seeds.rb>Login instructions here.</a>
**Screenshots**
It should look like this:
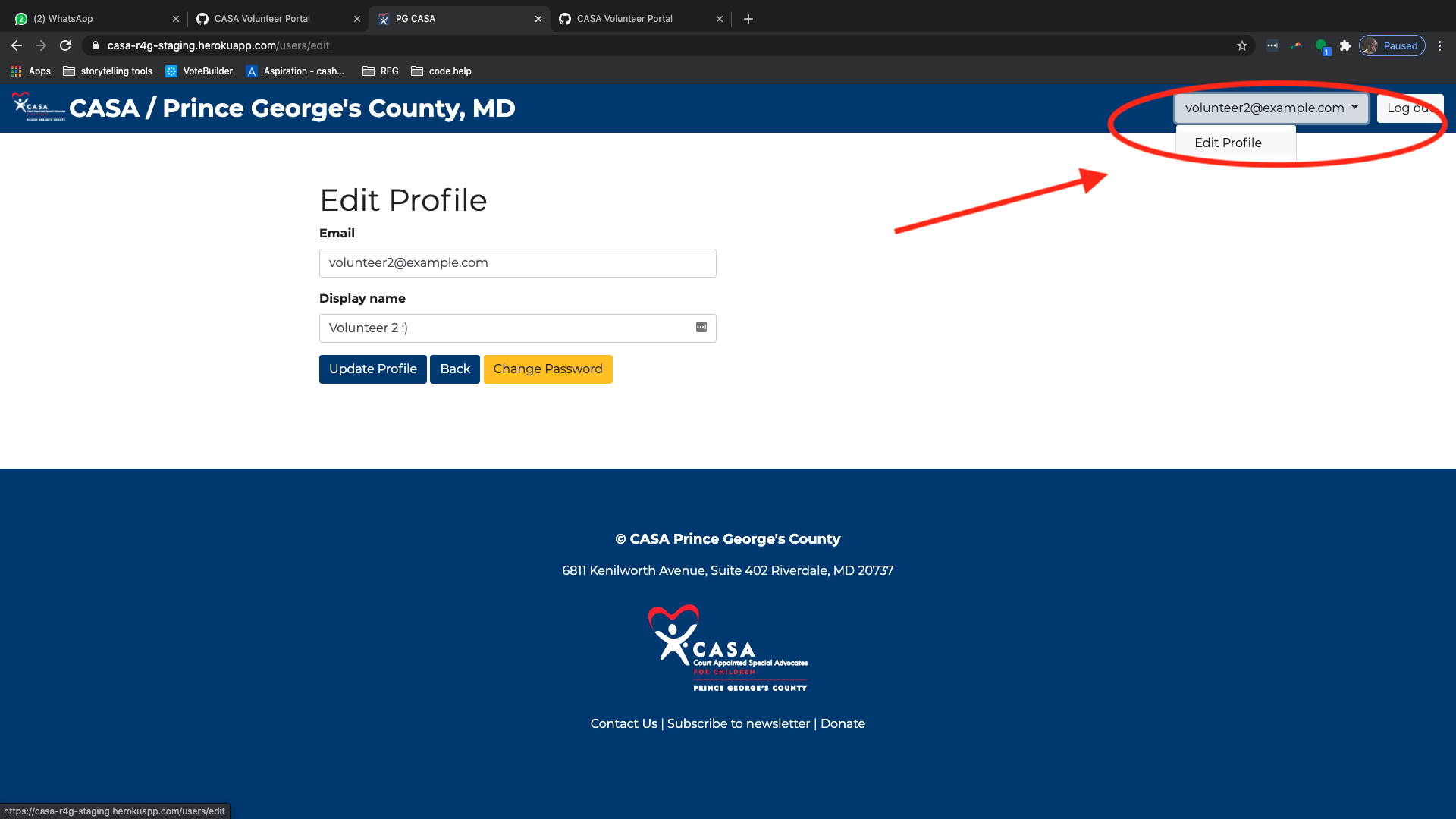
Relates to issues: #627, #628, #630 | design | make edit profile accessible by dropdown menu in all casa admin dashboard part of epic what type of user is this for all casa admin where does should this occur in the all casa admin dashboard dependent on description all casa admin needs an entry point to their edit profile page it should be accessible by clicking on their email in the upper right hand corner of their user dashboard when they click edit profile should appear as the only option in a drop down menu log in as any other user to see how this should look screenshots it should look like this relates to issues | 1 |
42,769 | 5,534,186,183 | IssuesEvent | 2017-03-21 14:55:43 | mozilla/addons-server | https://api.github.com/repos/mozilla/addons-server | closed | "Prev" screenshots navigation arrows are displayed for a moment at page refresh | component: redesign priority: enhancement triaged | Steps to reproduce:
1. Load details page for an add-on with screenshots i.e. https://addons.mozilla.org/en-US/firefox/addon/smart-https/?src=hp-dl-featured
2. Refresh the page while observing the screenshots section
Expected results:
There are no display or layout issues.
Actual results:
"Prev" navigation arrows are displayed for a moment.
Notes/Issues:
Verified on FF51(Win 7). Issue is reproducing all around AMO servers.
Video for this issue:

| 1.0 | "Prev" screenshots navigation arrows are displayed for a moment at page refresh - Steps to reproduce:
1. Load details page for an add-on with screenshots i.e. https://addons.mozilla.org/en-US/firefox/addon/smart-https/?src=hp-dl-featured
2. Refresh the page while observing the screenshots section
Expected results:
There are no display or layout issues.
Actual results:
"Prev" navigation arrows are displayed for a moment.
Notes/Issues:
Verified on FF51(Win 7). Issue is reproducing all around AMO servers.
Video for this issue:

| design | prev screenshots navigation arrows are displayed for a moment at page refresh steps to reproduce load details page for an add on with screenshots i e refresh the page while observing the screenshots section expected results there are no display or layout issues actual results prev navigation arrows are displayed for a moment notes issues verified on win issue is reproducing all around amo servers video for this issue | 1 |
49,517 | 13,187,224,855 | IssuesEvent | 2020-08-13 02:44:40 | icecube-trac/tix3 | https://api.github.com/repos/icecube-trac/tix3 | opened | dst-extractor (Trac #1579) | Incomplete Migration Migrated from Trac combo reconstruction defect | <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1579">https://code.icecube.wisc.edu/ticket/1579</a>, reported by nega and owned by juancarlos</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:11:22",
"description": "Since we're no longer building `libdst-extractor.so` all of these things fail:\n\n{{{\n~/i3/combo/build 14h 59m 59s\n\u276f ag 'load.*dst-extractor' ../src/\n../src/dst-extractor/python/__init__.py\n4:icetray.load('dst-extractor', False)\n\n../src/dst-extractor/resources/scripts/dstread09.py\n15:load(\"libdst-extractor\")\n\n../src/dst-extractor/resources/scripts/dstread08.py\n13:load(\"libdst-extractor\")\n\n../src/dst-extractor/resources/scripts/dst11_process.py\n82: load(\"libdst-extractor\")\n\n../src/dst-extractor/resources/scripts/dstread11.py\n15:load(\"libdst-extractor\")\n\n../src/dst-extractor/resources/scripts/dstread10.py\n13:load(\"libdst-extractor\")\n\n../src/dst-extractor/resources/scripts/dstread07.py\n12:load(\"libdst-extractor\")\n\n../src/filterscripts/resources/scripts/MinBiasHunter.py\n21:I3Tray.load(\"dst-extractor\")\n\n~/i3/combo/build 46s\n\u276f \n}}}\n\nThis also prevents the building of the documentation.\n",
"reporter": "nega",
"cc": "olivas, hdembinski",
"resolution": "fixed",
"_ts": "1550067082284240",
"component": "combo reconstruction",
"summary": "dst-extractor",
"priority": "blocker",
"keywords": "dst dst-extractor pybindings documentatoin",
"time": "2016-03-07T19:10:52",
"milestone": "",
"owner": "juancarlos",
"type": "defect"
}
```
</p>
</details>
| 1.0 | dst-extractor (Trac #1579) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1579">https://code.icecube.wisc.edu/ticket/1579</a>, reported by nega and owned by juancarlos</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:11:22",
"description": "Since we're no longer building `libdst-extractor.so` all of these things fail:\n\n{{{\n~/i3/combo/build 14h 59m 59s\n\u276f ag 'load.*dst-extractor' ../src/\n../src/dst-extractor/python/__init__.py\n4:icetray.load('dst-extractor', False)\n\n../src/dst-extractor/resources/scripts/dstread09.py\n15:load(\"libdst-extractor\")\n\n../src/dst-extractor/resources/scripts/dstread08.py\n13:load(\"libdst-extractor\")\n\n../src/dst-extractor/resources/scripts/dst11_process.py\n82: load(\"libdst-extractor\")\n\n../src/dst-extractor/resources/scripts/dstread11.py\n15:load(\"libdst-extractor\")\n\n../src/dst-extractor/resources/scripts/dstread10.py\n13:load(\"libdst-extractor\")\n\n../src/dst-extractor/resources/scripts/dstread07.py\n12:load(\"libdst-extractor\")\n\n../src/filterscripts/resources/scripts/MinBiasHunter.py\n21:I3Tray.load(\"dst-extractor\")\n\n~/i3/combo/build 46s\n\u276f \n}}}\n\nThis also prevents the building of the documentation.\n",
"reporter": "nega",
"cc": "olivas, hdembinski",
"resolution": "fixed",
"_ts": "1550067082284240",
"component": "combo reconstruction",
"summary": "dst-extractor",
"priority": "blocker",
"keywords": "dst dst-extractor pybindings documentatoin",
"time": "2016-03-07T19:10:52",
"milestone": "",
"owner": "juancarlos",
"type": "defect"
}
```
</p>
</details>
| non_design | dst extractor trac migrated from json status closed changetime description since we re no longer building libdst extractor so all of these things fail n n n combo build n ag load dst extractor src n src dst extractor python init py icetray load dst extractor false n n src dst extractor resources scripts py load libdst extractor n n src dst extractor resources scripts py load libdst extractor n n src dst extractor resources scripts process py load libdst extractor n n src dst extractor resources scripts py load libdst extractor n n src dst extractor resources scripts py load libdst extractor n n src dst extractor resources scripts py load libdst extractor n n src filterscripts resources scripts minbiashunter py load dst extractor n n combo build n n n nthis also prevents the building of the documentation n reporter nega cc olivas hdembinski resolution fixed ts component combo reconstruction summary dst extractor priority blocker keywords dst dst extractor pybindings documentatoin time milestone owner juancarlos type defect | 0 |
364,525 | 25,494,023,588 | IssuesEvent | 2022-11-27 12:56:49 | StraykerPL/RockPaperScissors | https://api.github.com/repos/StraykerPL/RockPaperScissors | opened | Feature: Add Testing label to repo | documentation | **Is your feature request related to a problem? Please describe.**
There's no `testing` label for checking general parts of product.
**Describe the solution you'd like**
Add `testing` label in GitHub, with description `This need to be tested`.
**Describe alternatives you've considered**
**Additional context**
| 1.0 | Feature: Add Testing label to repo - **Is your feature request related to a problem? Please describe.**
There's no `testing` label for checking general parts of product.
**Describe the solution you'd like**
Add `testing` label in GitHub, with description `This need to be tested`.
**Describe alternatives you've considered**
**Additional context**
| non_design | feature add testing label to repo is your feature request related to a problem please describe there s no testing label for checking general parts of product describe the solution you d like add testing label in github with description this need to be tested describe alternatives you ve considered additional context | 0 |
8,517 | 2,874,865,608 | IssuesEvent | 2015-06-09 02:20:36 | mozilla/thimble.webmaker.org | https://api.github.com/repos/mozilla/thimble.webmaker.org | closed | UX exploration for exposing files in a Project | design UX | We need to figure out how we'll handle files and projects. Specifically:
* How does a user toggle or expose the file view?
* How are files in a project displayed?
* How are files added, deleted and renamed?
* Can we just lean on native Brackets functionality here?
* How does a user open one of their existing projects?
* How does a user save & name their current project?
* How does a user delete their projects?
| 1.0 | UX exploration for exposing files in a Project - We need to figure out how we'll handle files and projects. Specifically:
* How does a user toggle or expose the file view?
* How are files in a project displayed?
* How are files added, deleted and renamed?
* Can we just lean on native Brackets functionality here?
* How does a user open one of their existing projects?
* How does a user save & name their current project?
* How does a user delete their projects?
| design | ux exploration for exposing files in a project we need to figure out how we ll handle files and projects specifically how does a user toggle or expose the file view how are files in a project displayed how are files added deleted and renamed can we just lean on native brackets functionality here how does a user open one of their existing projects how does a user save name their current project how does a user delete their projects | 1 |
156,551 | 24,624,594,933 | IssuesEvent | 2022-10-16 10:56:54 | dotnet/efcore | https://api.github.com/repos/dotnet/efcore | closed | DbSet.AddRange not preserving order of list in sql database | closed-by-design customer-reported | What we are seeing is that the order is not preserved when we add a range of values.
### Steps to reproduce
1) Insert an list with a specific order. using an dbset addrange call.
2) Check database table to review order.
pseudo code:
```C#
static void TestAddRange()
{
List<TestTable> list = new List<TestTable>(5);
for(int i=4; i >= 0; i--)
list.Add(new TestTable{Name = "test", OrderBy = i+1};
List<TestTable> orderedlist = list.OrderBy(t => t.OrderBy);
context.TestTable.AddRange(orderedlist);
context.SaveChanges();
// alternate that fails as well
//foreach(var temp in orderedlist)
// context.TestTable.Add(temp);
//
//context.SaveChanges()
// alternate code that succeeds but results in 5 round trips to database.
//foreach(var temp in orderedlist)
//{
// context.TestTable.Add(temp);
// context.SaveChanges()
//}
}
```
Result in database
Id , OrderBy
1, 3
2 , 1
3, 4
4, 2
5, 5
### Further technical details
EF Core version: 1.1.0
Database Provider: Microsoft.EntityFrameworkCore.SqlServer
Operating system: Azure Service Fabric (.net 4.5.2)
IDE: (e.g. Visual Studio 2015)
| 1.0 | DbSet.AddRange not preserving order of list in sql database - What we are seeing is that the order is not preserved when we add a range of values.
### Steps to reproduce
1) Insert an list with a specific order. using an dbset addrange call.
2) Check database table to review order.
pseudo code:
```C#
static void TestAddRange()
{
List<TestTable> list = new List<TestTable>(5);
for(int i=4; i >= 0; i--)
list.Add(new TestTable{Name = "test", OrderBy = i+1};
List<TestTable> orderedlist = list.OrderBy(t => t.OrderBy);
context.TestTable.AddRange(orderedlist);
context.SaveChanges();
// alternate that fails as well
//foreach(var temp in orderedlist)
// context.TestTable.Add(temp);
//
//context.SaveChanges()
// alternate code that succeeds but results in 5 round trips to database.
//foreach(var temp in orderedlist)
//{
// context.TestTable.Add(temp);
// context.SaveChanges()
//}
}
```
Result in database
Id , OrderBy
1, 3
2 , 1
3, 4
4, 2
5, 5
### Further technical details
EF Core version: 1.1.0
Database Provider: Microsoft.EntityFrameworkCore.SqlServer
Operating system: Azure Service Fabric (.net 4.5.2)
IDE: (e.g. Visual Studio 2015)
| design | dbset addrange not preserving order of list in sql database what we are seeing is that the order is not preserved when we add a range of values steps to reproduce insert an list with a specific order using an dbset addrange call check database table to review order pseudo code c static void testaddrange list list new list for int i i i list add new testtable name test orderby i list orderedlist list orderby t t orderby context testtable addrange orderedlist context savechanges alternate that fails as well foreach var temp in orderedlist context testtable add temp context savechanges alternate code that succeeds but results in round trips to database foreach var temp in orderedlist context testtable add temp context savechanges result in database id orderby further technical details ef core version database provider microsoft entityframeworkcore sqlserver operating system azure service fabric net ide e g visual studio | 1 |
259,048 | 22,387,468,701 | IssuesEvent | 2022-06-17 02:39:28 | DaHoon06/Dotto | https://api.github.com/repos/DaHoon06/Dotto | opened | 게시글 목록 조회시 limit값에 따른 목록 불러오기 | ✔️ Test BACK | 게시글 조회시 프론트에서 보내주는 limit 값을 받아 해당하는 값만큼 목록을 프론트에 전달
확인사항
- [ ] 목록 조회시 limit값에 따른 쿼리 수정
- [ ] 테스트 | 1.0 | 게시글 목록 조회시 limit값에 따른 목록 불러오기 - 게시글 조회시 프론트에서 보내주는 limit 값을 받아 해당하는 값만큼 목록을 프론트에 전달
확인사항
- [ ] 목록 조회시 limit값에 따른 쿼리 수정
- [ ] 테스트 | non_design | 게시글 목록 조회시 limit값에 따른 목록 불러오기 게시글 조회시 프론트에서 보내주는 limit 값을 받아 해당하는 값만큼 목록을 프론트에 전달 확인사항 목록 조회시 limit값에 따른 쿼리 수정 테스트 | 0 |
8,205 | 2,870,369,635 | IssuesEvent | 2015-06-07 03:06:56 | sunlightlabs/design | https://api.github.com/repos/sunlightlabs/design | closed | As a designer, I can plan and prepare for stakeholder interviews for UFO | design | - [x] Identify stakeholders in the org
- [x] Develop stakeholder interview questions
- [x] Schedule interviews | 1.0 | As a designer, I can plan and prepare for stakeholder interviews for UFO - - [x] Identify stakeholders in the org
- [x] Develop stakeholder interview questions
- [x] Schedule interviews | design | as a designer i can plan and prepare for stakeholder interviews for ufo identify stakeholders in the org develop stakeholder interview questions schedule interviews | 1 |
139,068 | 20,767,057,271 | IssuesEvent | 2022-03-15 21:52:34 | scribe-org/Scribe-iOS | https://api.github.com/repos/scribe-org/Scribe-iOS | closed | Update App Store images to display Wikidata | design -next release- | ### Terms
- [X] I have searched [open and closed design issues](https://github.com/scribe-org/Scribe-iOS/issues?q=is%3Aissue+label%3Adesign)
- [X] I agree to follow Scribe-iOS' [Code of Conduct](https://github.com/scribe-org/Scribe-iOS/blob/main/.github/CODE_OF_CONDUCT.md)
### Description
Based on best practices discussed at [Wikidata Data Reuse Days](https://diff.wikimedia.org/event/wikidata-data-reuse-days-2022/), it would be good to include Wikidata's logo in the images for the App Store. This was removed when there were more images and the goal was to minimize how much the user needed to scroll, but from then there have been many improvements on the images. The open-source image will thus be changed to also include a notification about Scribe open data stance.
### Contribution
These changes will be pushed shortly, as this issue is for documentation purposes. | 1.0 | Update App Store images to display Wikidata - ### Terms
- [X] I have searched [open and closed design issues](https://github.com/scribe-org/Scribe-iOS/issues?q=is%3Aissue+label%3Adesign)
- [X] I agree to follow Scribe-iOS' [Code of Conduct](https://github.com/scribe-org/Scribe-iOS/blob/main/.github/CODE_OF_CONDUCT.md)
### Description
Based on best practices discussed at [Wikidata Data Reuse Days](https://diff.wikimedia.org/event/wikidata-data-reuse-days-2022/), it would be good to include Wikidata's logo in the images for the App Store. This was removed when there were more images and the goal was to minimize how much the user needed to scroll, but from then there have been many improvements on the images. The open-source image will thus be changed to also include a notification about Scribe open data stance.
### Contribution
These changes will be pushed shortly, as this issue is for documentation purposes. | design | update app store images to display wikidata terms i have searched i agree to follow scribe ios description based on best practices discussed at it would be good to include wikidata s logo in the images for the app store this was removed when there were more images and the goal was to minimize how much the user needed to scroll but from then there have been many improvements on the images the open source image will thus be changed to also include a notification about scribe open data stance contribution these changes will be pushed shortly as this issue is for documentation purposes | 1 |
70,862 | 13,541,309,579 | IssuesEvent | 2020-09-16 15:43:04 | vektorprogrammet/vektorprogrammet | https://api.github.com/repos/vektorprogrammet/vektorprogrammet | closed | Symfony Insight: Your project must not use PHP super globals | Code Quality | Another critical suggestion that must be fixed in order for Symfony Insight to pass on our PRs

| 1.0 | Symfony Insight: Your project must not use PHP super globals - Another critical suggestion that must be fixed in order for Symfony Insight to pass on our PRs

| non_design | symfony insight your project must not use php super globals another critical suggestion that must be fixed in order for symfony insight to pass on our prs | 0 |
26,755 | 27,160,830,753 | IssuesEvent | 2023-02-17 11:43:27 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | Impossible to resize collision shape for tile when vertex outside of tilesheet | bug topic:editor usability | **Godot version:**
v.3.1.2.stable.official
**OS/device including version:**
Pop!_OS 19.10 (highly derived from Ubuntu)
**Issue description:**
I am following the tilemap tutorial in the documentation and accidentally I created a collision shape (rectangular) in an Atlas tile which is bigger than the size of the tilesheet :
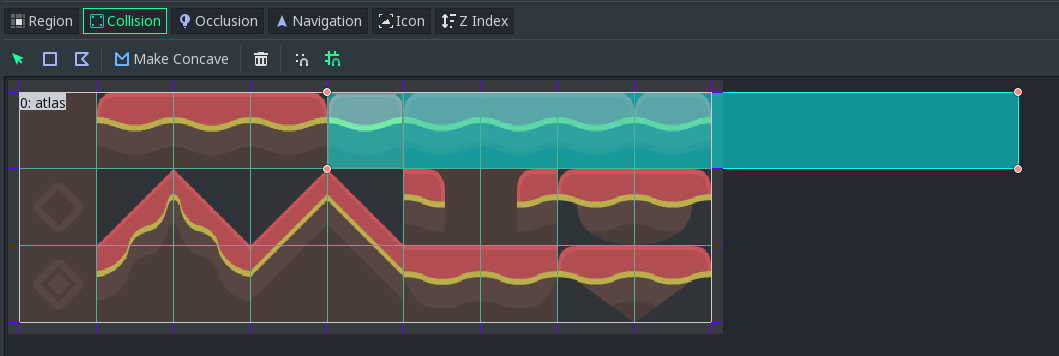
**Steps to reproduce:**
Now if I want to resize the rectangle collision shape to fit the tile, I can't select any vertex outside the tilesheet (but I can grab and move the two left corners).
**Minimal reproduction project:**
[tilemap.zip](https://github.com/godotengine/godot/files/4042642/tilemap.zip)
| True | Impossible to resize collision shape for tile when vertex outside of tilesheet - **Godot version:**
v.3.1.2.stable.official
**OS/device including version:**
Pop!_OS 19.10 (highly derived from Ubuntu)
**Issue description:**
I am following the tilemap tutorial in the documentation and accidentally I created a collision shape (rectangular) in an Atlas tile which is bigger than the size of the tilesheet :
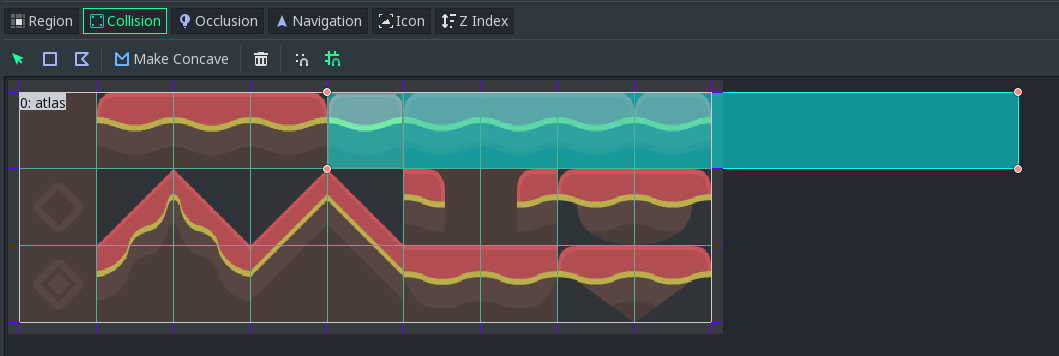
**Steps to reproduce:**
Now if I want to resize the rectangle collision shape to fit the tile, I can't select any vertex outside the tilesheet (but I can grab and move the two left corners).
**Minimal reproduction project:**
[tilemap.zip](https://github.com/godotengine/godot/files/4042642/tilemap.zip)
| non_design | impossible to resize collision shape for tile when vertex outside of tilesheet godot version v stable official os device including version pop os highly derived from ubuntu issue description i am following the tilemap tutorial in the documentation and accidentally i created a collision shape rectangular in an atlas tile which is bigger than the size of the tilesheet steps to reproduce now if i want to resize the rectangle collision shape to fit the tile i can t select any vertex outside the tilesheet but i can grab and move the two left corners minimal reproduction project | 0 |
134,466 | 19,211,210,687 | IssuesEvent | 2021-12-07 02:17:34 | CERT-Polska/mquery | https://api.github.com/repos/CERT-Polska/mquery | closed | When querying for a duplicate rule, warn the user | status:needs more design | **Feature Category**
- [ ] Correctness
- [x] User Interface / User Experience
- [x] Performance
- [ ] Other (please explain)
**Describe the problem**
It's possible for two independent users to use the same yara rule. Mquery will then start matching files, which is unnecessary because the result will be exactly the same.
**Describe the solution you'd like**
Not sure, because sometimes running the same query **is** what the user wants (for example, new files were indexed).
Probably popup/notification "hey, the same yara rule was already checked by someone 10 days ago - do you want to see it?". Or maybe redirect to the results.
It's harder than it looks like, because users can select tags when querying. :thinking:.
**Describe alternatives you've considered**
Don't change anything. Keep it simple. | 1.0 | When querying for a duplicate rule, warn the user - **Feature Category**
- [ ] Correctness
- [x] User Interface / User Experience
- [x] Performance
- [ ] Other (please explain)
**Describe the problem**
It's possible for two independent users to use the same yara rule. Mquery will then start matching files, which is unnecessary because the result will be exactly the same.
**Describe the solution you'd like**
Not sure, because sometimes running the same query **is** what the user wants (for example, new files were indexed).
Probably popup/notification "hey, the same yara rule was already checked by someone 10 days ago - do you want to see it?". Or maybe redirect to the results.
It's harder than it looks like, because users can select tags when querying. :thinking:.
**Describe alternatives you've considered**
Don't change anything. Keep it simple. | design | when querying for a duplicate rule warn the user feature category correctness user interface user experience performance other please explain describe the problem it s possible for two independent users to use the same yara rule mquery will then start matching files which is unnecessary because the result will be exactly the same describe the solution you d like not sure because sometimes running the same query is what the user wants for example new files were indexed probably popup notification hey the same yara rule was already checked by someone days ago do you want to see it or maybe redirect to the results it s harder than it looks like because users can select tags when querying thinking describe alternatives you ve considered don t change anything keep it simple | 1 |
42,080 | 17,025,770,598 | IssuesEvent | 2021-07-03 13:24:49 | FirebirdSQL/jaybird | https://api.github.com/repos/FirebirdSQL/jaybird | closed | Support nbackup fixup and preserve sequence option | component: services api fix-version: Jaybird 5 type: new feature | Firebird 4 added support for the fixup (nbackup -F) option (which switches the database back to the 'normal' state), and introduced the `-sequence` option which will preserve the current database guid and replication sequence information on restore or fixup.
Add support for this in the `NBackupManager` API. | 1.0 | Support nbackup fixup and preserve sequence option - Firebird 4 added support for the fixup (nbackup -F) option (which switches the database back to the 'normal' state), and introduced the `-sequence` option which will preserve the current database guid and replication sequence information on restore or fixup.
Add support for this in the `NBackupManager` API. | non_design | support nbackup fixup and preserve sequence option firebird added support for the fixup nbackup f option which switches the database back to the normal state and introduced the sequence option which will preserve the current database guid and replication sequence information on restore or fixup add support for this in the nbackupmanager api | 0 |
49,177 | 6,153,778,522 | IssuesEvent | 2017-06-28 10:51:57 | SAP/techne | https://api.github.com/repos/SAP/techne | closed | Define Spacing types | design UX | Goal: Identify and define most of the spacing used on the components.
### Taks
- [x] Identify spacing for [sections](https://github.com/SAP/techne/wiki/Website-Content-Components#content-components)
- [x] Identify for [inputs elements](https://github.com/SAP/techne/wiki/Form-Inputs)
- [x] Identify spacing for [cards](https://github.com/SAP/techne/issues/678#issuecomment-305724490)
- [x] Define reusable spacing names
- [x] Add Results to the Wiki https://github.com/SAP/techne/wiki/Sapcing-Design-specs
| 1.0 | Define Spacing types - Goal: Identify and define most of the spacing used on the components.
### Taks
- [x] Identify spacing for [sections](https://github.com/SAP/techne/wiki/Website-Content-Components#content-components)
- [x] Identify for [inputs elements](https://github.com/SAP/techne/wiki/Form-Inputs)
- [x] Identify spacing for [cards](https://github.com/SAP/techne/issues/678#issuecomment-305724490)
- [x] Define reusable spacing names
- [x] Add Results to the Wiki https://github.com/SAP/techne/wiki/Sapcing-Design-specs
| design | define spacing types goal identify and define most of the spacing used on the components taks identify spacing for identify for identify spacing for define reusable spacing names add results to the wiki | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.