Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
267,139 | 20,190,955,050 | IssuesEvent | 2022-02-11 05:20:59 | vercel/next.js | https://api.github.com/repos/vercel/next.js | opened | Docs: Add version select in Next.js Docs | template: documentation | ### What is the improvement or update you wish to see?
I can access to prev version Docs with changing path to `/docs/tag/$VERSION`.
But It is hard to change my version.
If there is a select input for change version of Doc, Most of users would be joyful including me.
### Is there any context that might help us understand?
It is about documentation usability.
### Does the docs page already exist? Please link to it.
_No response_ | 1.0 | Docs: Add version select in Next.js Docs - ### What is the improvement or update you wish to see?
I can access to prev version Docs with changing path to `/docs/tag/$VERSION`.
But It is hard to change my version.
If there is a select input for change version of Doc, Most of users would be joyful including me.
### Is there any context that might help us understand?
It is about documentation usability.
### Does the docs page already exist? Please link to it.
_No response_ | non_priority | docs add version select in next js docs what is the improvement or update you wish to see i can access to prev version docs with changing path to docs tag version but it is hard to change my version if there is a select input for change version of doc most of users would be joyful including me is there any context that might help us understand it is about documentation usability does the docs page already exist please link to it no response | 0 |
265,886 | 23,207,491,333 | IssuesEvent | 2022-08-02 07:10:42 | wso2/product-is | https://api.github.com/repos/wso2/product-is | opened | [New feature testing] Magic link | test | **Is your suggestion a test requirement/change or improvements of the test framework? Please describe.**
Required to test new feature magic link
**Describe the solution you would prefer**
- [ ] Create test plan
- [ ] Add configurations
- [ ] Execute test
- [ ] Result analysing and issue reporting
### Optional Fields
**Additional context**
<!-- Add any other context or screenshots about the test automation request here. e.g User scenario guide, functional Requirement Specifications (FRS) Documents -->
**Related Issues:**
<!-- Any related issues from this/other repositories-->
| 1.0 | [New feature testing] Magic link - **Is your suggestion a test requirement/change or improvements of the test framework? Please describe.**
Required to test new feature magic link
**Describe the solution you would prefer**
- [ ] Create test plan
- [ ] Add configurations
- [ ] Execute test
- [ ] Result analysing and issue reporting
### Optional Fields
**Additional context**
<!-- Add any other context or screenshots about the test automation request here. e.g User scenario guide, functional Requirement Specifications (FRS) Documents -->
**Related Issues:**
<!-- Any related issues from this/other repositories-->
| non_priority | magic link is your suggestion a test requirement change or improvements of the test framework please describe required to test new feature magic link describe the solution you would prefer create test plan add configurations execute test result analysing and issue reporting optional fields additional context related issues | 0 |
417,664 | 28,110,751,621 | IssuesEvent | 2023-03-31 06:58:04 | jundatan/ped | https://api.github.com/repos/jundatan/ped | opened | Bug Report: UG picture example | severity.VeryLow type.DocumentationBug | 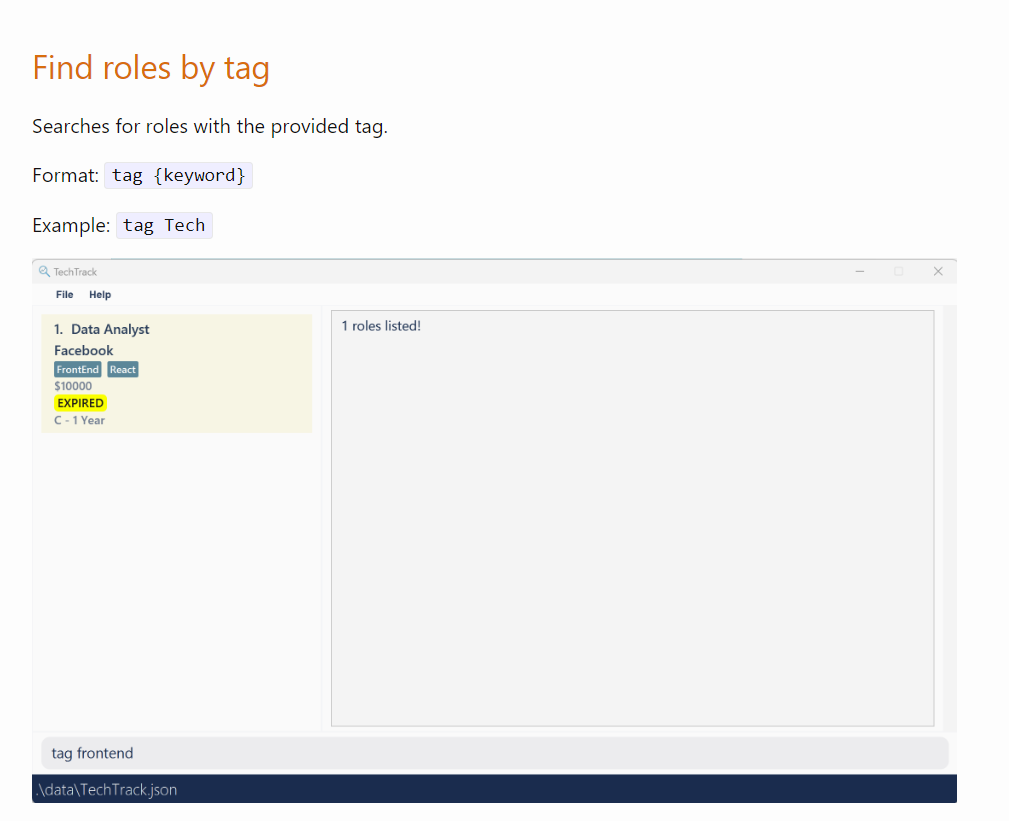
Picture does not match the example. Potential UG bug.
<!--session: 1680242417179-b127148a-0d0d-43d7-b0dd-505a78612d30-->
<!--Version: Web v3.4.7--> | 1.0 | Bug Report: UG picture example - 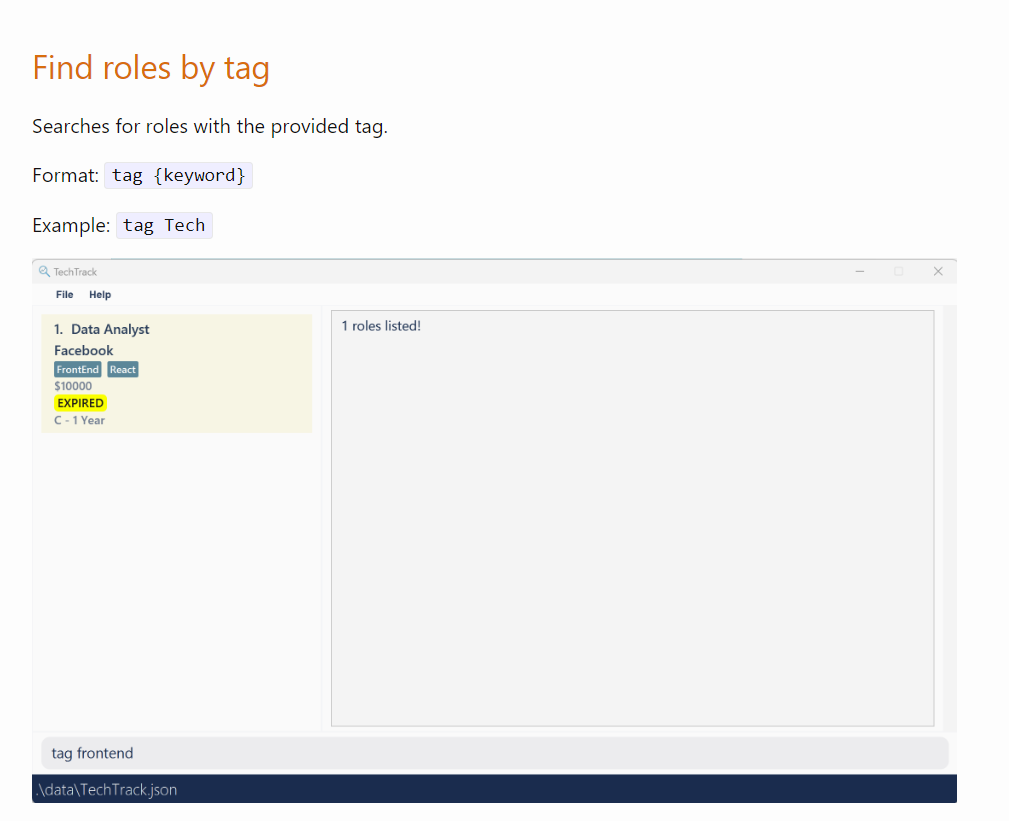
Picture does not match the example. Potential UG bug.
<!--session: 1680242417179-b127148a-0d0d-43d7-b0dd-505a78612d30-->
<!--Version: Web v3.4.7--> | non_priority | bug report ug picture example picture does not match the example potential ug bug | 0 |
222,924 | 17,097,290,142 | IssuesEvent | 2021-07-09 05:56:29 | MisterGuinness/gnome-shell-extension-sensors | https://api.github.com/repos/MisterGuinness/gnome-shell-extension-sensors | closed | Manual installation repository is wrong | documentation | The manual installation instruction to clone the source repository is still referring to the original repository, it should reference
`https://github.com/MisterGuinness/gnome-shell-extension-sensors` | 1.0 | Manual installation repository is wrong - The manual installation instruction to clone the source repository is still referring to the original repository, it should reference
`https://github.com/MisterGuinness/gnome-shell-extension-sensors` | non_priority | manual installation repository is wrong the manual installation instruction to clone the source repository is still referring to the original repository it should reference | 0 |
1,239 | 3,089,423,146 | IssuesEvent | 2015-08-25 21:25:29 | dotnet/wcf | https://api.github.com/repos/dotnet/wcf | closed | Fix https tests that fail when Bridge runs remotely | Infrastructure test bug | All the https OuterLoop tests fail when the Bridge is run remotely. Investigate and solve. | 1.0 | Fix https tests that fail when Bridge runs remotely - All the https OuterLoop tests fail when the Bridge is run remotely. Investigate and solve. | non_priority | fix https tests that fail when bridge runs remotely all the https outerloop tests fail when the bridge is run remotely investigate and solve | 0 |
190,243 | 15,223,997,219 | IssuesEvent | 2021-02-18 04:05:44 | lucasstarsz/Slope-ECS | https://api.github.com/repos/lucasstarsz/Slope-ECS | closed | Add examples of how to use the ECS | documentation finished | The ECS, while it is available on Maven Central, does not have any explanations or examples of how to use it.
This is an integral part of what a repository should contain -- it needs to be added as soon as possible. | 1.0 | Add examples of how to use the ECS - The ECS, while it is available on Maven Central, does not have any explanations or examples of how to use it.
This is an integral part of what a repository should contain -- it needs to be added as soon as possible. | non_priority | add examples of how to use the ecs the ecs while it is available on maven central does not have any explanations or examples of how to use it this is an integral part of what a repository should contain it needs to be added as soon as possible | 0 |
47,410 | 13,223,359,295 | IssuesEvent | 2020-08-17 17:05:09 | ipfs/go-ipfs | https://api.github.com/repos/ipfs/go-ipfs | closed | Deprecate & remove Secio security transport | P0 backwards incompatible: protocol epic kind/enhancement status/ready topic/security topic/tracking | Now that IPFS has support for TLS and Noise, it's time to complete the process of deprecating and removing support for Secio. This issue is for tracking the rollout.
**Please upgrade IPFS ASAP to stay connected!** If you are having issues upgrading please let us know here.
### Planned releases
**Target version of Secio removal**: **0.7**
### History of security support changes
> Each update contains the security protocol listed by default priority.
**Go IPFS**
<0.4.21: Secio
0.4.21: Secio > TLS1.3 _(May 31, 2019)_
0.5.0: TLS1.3 > Secio _(April 28, 2020)_
0.6.0: TLS1.3 > Secio > Noise _(June 20, 2020)_
**JS IPFS**
<0.47.0: Secio
0.47.0: Secio > Noise (June 24, 2020)
### BREAKING CHANGES
Removal of Secio will result in the following:
- Go IPFS nodes older than 0.4.21 will not be able to communicate with Go IPFS nodes >= **0.7**.
- Go IPFS nodes older than 0.5.0 with TLS support will require an additional round trip when creating a connection with GO IPFS nodes >= **0.7** (this is due to failing to negotiate Secio and falling back to TLS1.3)
- JS IPFS nodes older than 0.47 will not be able to communicate with GO IPFS nodes >= **0.7**.
### Testing
- Prior to removing support for Secio we will do thorough testing of the DHT to ensure we are maintaining performance added in 0.5.
### References
- https://blog.ipfs.io/2020-08-07-deprecating-secio/ | True | Deprecate & remove Secio security transport - Now that IPFS has support for TLS and Noise, it's time to complete the process of deprecating and removing support for Secio. This issue is for tracking the rollout.
**Please upgrade IPFS ASAP to stay connected!** If you are having issues upgrading please let us know here.
### Planned releases
**Target version of Secio removal**: **0.7**
### History of security support changes
> Each update contains the security protocol listed by default priority.
**Go IPFS**
<0.4.21: Secio
0.4.21: Secio > TLS1.3 _(May 31, 2019)_
0.5.0: TLS1.3 > Secio _(April 28, 2020)_
0.6.0: TLS1.3 > Secio > Noise _(June 20, 2020)_
**JS IPFS**
<0.47.0: Secio
0.47.0: Secio > Noise (June 24, 2020)
### BREAKING CHANGES
Removal of Secio will result in the following:
- Go IPFS nodes older than 0.4.21 will not be able to communicate with Go IPFS nodes >= **0.7**.
- Go IPFS nodes older than 0.5.0 with TLS support will require an additional round trip when creating a connection with GO IPFS nodes >= **0.7** (this is due to failing to negotiate Secio and falling back to TLS1.3)
- JS IPFS nodes older than 0.47 will not be able to communicate with GO IPFS nodes >= **0.7**.
### Testing
- Prior to removing support for Secio we will do thorough testing of the DHT to ensure we are maintaining performance added in 0.5.
### References
- https://blog.ipfs.io/2020-08-07-deprecating-secio/ | non_priority | deprecate remove secio security transport now that ipfs has support for tls and noise it s time to complete the process of deprecating and removing support for secio this issue is for tracking the rollout please upgrade ipfs asap to stay connected if you are having issues upgrading please let us know here planned releases target version of secio removal history of security support changes each update contains the security protocol listed by default priority go ipfs secio secio may secio april secio noise june js ipfs secio secio noise june breaking changes removal of secio will result in the following go ipfs nodes older than will not be able to communicate with go ipfs nodes go ipfs nodes older than with tls support will require an additional round trip when creating a connection with go ipfs nodes this is due to failing to negotiate secio and falling back to js ipfs nodes older than will not be able to communicate with go ipfs nodes testing prior to removing support for secio we will do thorough testing of the dht to ensure we are maintaining performance added in references | 0 |
83,129 | 10,321,365,451 | IssuesEvent | 2019-08-31 01:17:03 | ponydevs/pixel.horse | https://api.github.com/repos/ponydevs/pixel.horse | opened | Discussion: Community Management of Feature Requests | documentation help wanted question | We need a platform where people can make feature requests and upvote other people's feature requests. This allows duplicate feature requests to be merged and for popular ones to bubble up and be addressed by the dev team. Discord uses "uservoice", but this isn't a viable option for us.
This Quora answer lists some possible alternatives we could use: https://www.quora.com/What-is-the-best-alternative-to-uservoice-to-get-and-manage-customer-feedback-for-a-website | 1.0 | Discussion: Community Management of Feature Requests - We need a platform where people can make feature requests and upvote other people's feature requests. This allows duplicate feature requests to be merged and for popular ones to bubble up and be addressed by the dev team. Discord uses "uservoice", but this isn't a viable option for us.
This Quora answer lists some possible alternatives we could use: https://www.quora.com/What-is-the-best-alternative-to-uservoice-to-get-and-manage-customer-feedback-for-a-website | non_priority | discussion community management of feature requests we need a platform where people can make feature requests and upvote other people s feature requests this allows duplicate feature requests to be merged and for popular ones to bubble up and be addressed by the dev team discord uses uservoice but this isn t a viable option for us this quora answer lists some possible alternatives we could use | 0 |
334,614 | 24,427,900,212 | IssuesEvent | 2022-10-06 05:29:42 | Clueless-Community/clueless-official-website | https://api.github.com/repos/Clueless-Community/clueless-official-website | closed | Addition : Issue template 🛠 | documentation good first issue hacktoberfest | ## What i am suggesting to add ?
I am suggesting to add **Issue Templates** to the repository, it can be as many categories as needed - primary categories of issues are mostly : `bugs`, `docs`, `general feature` and so on.
## Why to add it ?
Adding an issue Template allows you to organize the issues made by folks in a much better way.
- We can know if someone wants to add a feature.
- We can know if someone wants to write a test or maybe fix something in the website
- Here's a general idea :

## Can i work on it ?
Yes, i will be glad to help an Opensource project grow more ! | 1.0 | Addition : Issue template 🛠 - ## What i am suggesting to add ?
I am suggesting to add **Issue Templates** to the repository, it can be as many categories as needed - primary categories of issues are mostly : `bugs`, `docs`, `general feature` and so on.
## Why to add it ?
Adding an issue Template allows you to organize the issues made by folks in a much better way.
- We can know if someone wants to add a feature.
- We can know if someone wants to write a test or maybe fix something in the website
- Here's a general idea :

## Can i work on it ?
Yes, i will be glad to help an Opensource project grow more ! | non_priority | addition issue template 🛠 what i am suggesting to add i am suggesting to add issue templates to the repository it can be as many categories as needed primary categories of issues are mostly bugs docs general feature and so on why to add it adding an issue template allows you to organize the issues made by folks in a much better way we can know if someone wants to add a feature we can know if someone wants to write a test or maybe fix something in the website here s a general idea can i work on it yes i will be glad to help an opensource project grow more | 0 |
75,962 | 21,082,524,425 | IssuesEvent | 2022-04-03 05:19:33 | quicklisp/quicklisp-projects | https://api.github.com/repos/quicklisp/quicklisp-projects | closed | Please add one-more-re-nightmare | canbuild | one-more-re-nightmare is a regular expression compiler. It lives at <https://github.com/telekons/one-more-re-nightmare>.
There are three systems:
- `one-more-re-nightmare`, the compiler
- `one-more-re-nightmare-tests`, a test suite and fuzz tester, and
- `one-more-re-nightmare-simd`, which adds SIMD acceleration for tight loops in generated code.
The last system is dependent on SBCL 2.1.10 or later on x86-64 with AVX2, the other two should run on any Common Lisp system. | 1.0 | Please add one-more-re-nightmare - one-more-re-nightmare is a regular expression compiler. It lives at <https://github.com/telekons/one-more-re-nightmare>.
There are three systems:
- `one-more-re-nightmare`, the compiler
- `one-more-re-nightmare-tests`, a test suite and fuzz tester, and
- `one-more-re-nightmare-simd`, which adds SIMD acceleration for tight loops in generated code.
The last system is dependent on SBCL 2.1.10 or later on x86-64 with AVX2, the other two should run on any Common Lisp system. | non_priority | please add one more re nightmare one more re nightmare is a regular expression compiler it lives at there are three systems one more re nightmare the compiler one more re nightmare tests a test suite and fuzz tester and one more re nightmare simd which adds simd acceleration for tight loops in generated code the last system is dependent on sbcl or later on with the other two should run on any common lisp system | 0 |
84,160 | 24,245,173,442 | IssuesEvent | 2022-09-27 09:57:14 | adoptium/ci-jenkins-pipelines | https://api.github.com/repos/adoptium/ci-jenkins-pipelines | opened | Be able to build with a tag for ci-jenkins-pipeline repo, rather than use "master" for branch | enhancement reproduciblebuild | To be able to have reproducible build, we need to have fixed git tag on each repo, including ci-jenkins-pipeline, temurin-build and each jdk source repo.
https://github.com/adoptium/temurin-build/issues/3091 has covered the jdk source repo
https://github.com/adoptium/temurin-build/issues/3103 has covered temurin-build part.
this issue is for the ci-jenkins-pipeline part.
` "pipeline_branch": `should be set to a git tag
Related to old issue https://github.com/adoptium/ci-jenkins-pipelines/issues/46 | 1.0 | Be able to build with a tag for ci-jenkins-pipeline repo, rather than use "master" for branch - To be able to have reproducible build, we need to have fixed git tag on each repo, including ci-jenkins-pipeline, temurin-build and each jdk source repo.
https://github.com/adoptium/temurin-build/issues/3091 has covered the jdk source repo
https://github.com/adoptium/temurin-build/issues/3103 has covered temurin-build part.
this issue is for the ci-jenkins-pipeline part.
` "pipeline_branch": `should be set to a git tag
Related to old issue https://github.com/adoptium/ci-jenkins-pipelines/issues/46 | non_priority | be able to build with a tag for ci jenkins pipeline repo rather than use master for branch to be able to have reproducible build we need to have fixed git tag on each repo including ci jenkins pipeline temurin build and each jdk source repo has covered the jdk source repo has covered temurin build part this issue is for the ci jenkins pipeline part pipeline branch should be set to a git tag related to old issue | 0 |
53,854 | 13,262,391,383 | IssuesEvent | 2020-08-20 21:41:57 | icecube-trac/tix4 | https://api.github.com/repos/icecube-trac/tix4 | closed | [filterscripts] L2 Monopole Reconstruction throws (Trac #2198) | Migrated from Trac combo reconstruction defect | L2 monopole reconstruction is throwing...
File "/home/olivas/icecube/combo/cisystem/build/lib/icecube/filterscripts/offlineL2/level2_Reconstruction_Monopole.py", line 328, in <lambda>
If = lambda f: "FilterMask" in f and f["FilterMask"][filter_globals.MonopoleFilter].condition_passed and If(f)
RuntimeError: maximum recursion depth exceeded while calling a Python object
I'm guessing this is related to recent activity by flambda.
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/2198">https://code.icecube.wisc.edu/projects/icecube/ticket/2198</a>, reported by olivasand owned by flauber</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:15:18",
"_ts": "1550067318169976",
"description": "L2 monopole reconstruction is throwing...\n\n\n File \"/home/olivas/icecube/combo/cisystem/build/lib/icecube/filterscripts/offlineL2/level2_Reconstruction_Monopole.py\", line 328, in <lambda>\n If = lambda f: \"FilterMask\" in f and f[\"FilterMask\"][filter_globals.MonopoleFilter].condition_passed and If(f)\nRuntimeError: maximum recursion depth exceeded while calling a Python object\n\n\nI'm guessing this is related to recent activity by flambda.",
"reporter": "olivas",
"cc": "blaufuss",
"resolution": "fixed",
"time": "2018-10-11T16:15:21",
"component": "combo reconstruction",
"summary": "[filterscripts] L2 Monopole Reconstruction throws",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "flauber",
"type": "defect"
}
```
</p>
</details>
| 1.0 | [filterscripts] L2 Monopole Reconstruction throws (Trac #2198) - L2 monopole reconstruction is throwing...
File "/home/olivas/icecube/combo/cisystem/build/lib/icecube/filterscripts/offlineL2/level2_Reconstruction_Monopole.py", line 328, in <lambda>
If = lambda f: "FilterMask" in f and f["FilterMask"][filter_globals.MonopoleFilter].condition_passed and If(f)
RuntimeError: maximum recursion depth exceeded while calling a Python object
I'm guessing this is related to recent activity by flambda.
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/2198">https://code.icecube.wisc.edu/projects/icecube/ticket/2198</a>, reported by olivasand owned by flauber</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:15:18",
"_ts": "1550067318169976",
"description": "L2 monopole reconstruction is throwing...\n\n\n File \"/home/olivas/icecube/combo/cisystem/build/lib/icecube/filterscripts/offlineL2/level2_Reconstruction_Monopole.py\", line 328, in <lambda>\n If = lambda f: \"FilterMask\" in f and f[\"FilterMask\"][filter_globals.MonopoleFilter].condition_passed and If(f)\nRuntimeError: maximum recursion depth exceeded while calling a Python object\n\n\nI'm guessing this is related to recent activity by flambda.",
"reporter": "olivas",
"cc": "blaufuss",
"resolution": "fixed",
"time": "2018-10-11T16:15:21",
"component": "combo reconstruction",
"summary": "[filterscripts] L2 Monopole Reconstruction throws",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "flauber",
"type": "defect"
}
```
</p>
</details>
| non_priority | monopole reconstruction throws trac monopole reconstruction is throwing file home olivas icecube combo cisystem build lib icecube filterscripts reconstruction monopole py line in if lambda f filtermask in f and f condition passed and if f runtimeerror maximum recursion depth exceeded while calling a python object i m guessing this is related to recent activity by flambda migrated from json status closed changetime ts description monopole reconstruction is throwing n n n file home olivas icecube combo cisystem build lib icecube filterscripts reconstruction monopole py line in n if lambda f filtermask in f and f condition passed and if f nruntimeerror maximum recursion depth exceeded while calling a python object n n ni m guessing this is related to recent activity by flambda reporter olivas cc blaufuss resolution fixed time component combo reconstruction summary monopole reconstruction throws priority normal keywords milestone owner flauber type defect | 0 |
129,887 | 27,582,321,214 | IssuesEvent | 2023-03-08 17:01:36 | FerretDB/FerretDB | https://api.github.com/repos/FerretDB/FerretDB | closed | Format index names in PG, so the length limit is not reached | code/chore | With table names like `TestInsertCompat-InsertUnorderedOneError-InsertMany_St_4c6d95fa` the "default" index name could be something like `TestInsertCompat-InsertUnorderedOneError-InsertMany_St_4c6d95fa_field`, and then we reach the limit of index name. In such case, PG automatically truncates it, and it produces the same name for everything.
We should find a way to create indexes for long table names.
One possible option is not format index names in a similar way to how we format collection->table names, so we ensure that the index name is not too long.
Metadata to consider storing:
- v
- key
- name
- unique | 1.0 | Format index names in PG, so the length limit is not reached - With table names like `TestInsertCompat-InsertUnorderedOneError-InsertMany_St_4c6d95fa` the "default" index name could be something like `TestInsertCompat-InsertUnorderedOneError-InsertMany_St_4c6d95fa_field`, and then we reach the limit of index name. In such case, PG automatically truncates it, and it produces the same name for everything.
We should find a way to create indexes for long table names.
One possible option is not format index names in a similar way to how we format collection->table names, so we ensure that the index name is not too long.
Metadata to consider storing:
- v
- key
- name
- unique | non_priority | format index names in pg so the length limit is not reached with table names like testinsertcompat insertunorderedoneerror insertmany st the default index name could be something like testinsertcompat insertunorderedoneerror insertmany st field and then we reach the limit of index name in such case pg automatically truncates it and it produces the same name for everything we should find a way to create indexes for long table names one possible option is not format index names in a similar way to how we format collection table names so we ensure that the index name is not too long metadata to consider storing v key name unique | 0 |
281,206 | 30,888,407,518 | IssuesEvent | 2023-08-04 01:17:08 | hshivhare67/kernel_v4.1.15 | https://api.github.com/repos/hshivhare67/kernel_v4.1.15 | reopened | CVE-2020-29371 (Low) detected in linuxlinux-4.6 | Mend: dependency security vulnerability | ## CVE-2020-29371 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/romfs/storage.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/romfs/storage.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/romfs/storage.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in romfs_dev_read in fs/romfs/storage.c in the Linux kernel before 5.8.4. Uninitialized memory leaks to userspace, aka CID-bcf85fcedfdd.
<p>Publish Date: 2020-11-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-29371>CVE-2020-29371</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-29371">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-29371</a></p>
<p>Release Date: 2020-11-28</p>
<p>Fix Resolution: v5.9-rc2,v5.8.4,v5.7.18,v5.4.61</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-29371 (Low) detected in linuxlinux-4.6 - ## CVE-2020-29371 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/romfs/storage.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/romfs/storage.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/romfs/storage.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in romfs_dev_read in fs/romfs/storage.c in the Linux kernel before 5.8.4. Uninitialized memory leaks to userspace, aka CID-bcf85fcedfdd.
<p>Publish Date: 2020-11-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-29371>CVE-2020-29371</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-29371">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-29371</a></p>
<p>Release Date: 2020-11-28</p>
<p>Fix Resolution: v5.9-rc2,v5.8.4,v5.7.18,v5.4.61</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve low detected in linuxlinux cve low severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in base branch master vulnerable source files fs romfs storage c fs romfs storage c fs romfs storage c vulnerability details an issue was discovered in romfs dev read in fs romfs storage c in the linux kernel before uninitialized memory leaks to userspace aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
5,567 | 12,705,529,449 | IssuesEvent | 2020-06-23 04:56:06 | MicrosoftDocs/architecture-center | https://api.github.com/repos/MicrosoftDocs/architecture-center | closed | SignalR - Realtime Web Dashboard | Pri2 architecture-center/svc assigned-to-author doc-enhancement solution-idea/subsvc triaged |
It would be great if you can enhance this documentation with implementation details, pricing guidance, code examples, etc.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: ec994a02-c71a-8dea-8994-eb8c1e5e2992
* Version Independent ID: 2520c9c8-9d28-dd38-fa05-2c748b20ed8c
* Content: [Real-time Web Dashboard - Azure Solution Ideas](https://docs.microsoft.com/en-us/azure/architecture/solution-ideas/articles/real-time-web-dashboard)
* Content Source: [docs/solution-ideas/articles/real-time-web-dashboard.md](https://github.com/microsoftdocs/architecture-center/blob/master/docs/solution-ideas/articles/real-time-web-dashboard.md)
* Service: **architecture-center**
* Sub-service: **solution-idea**
* GitHub Login: @adamboeglin
* Microsoft Alias: **pnp** | 1.0 | SignalR - Realtime Web Dashboard -
It would be great if you can enhance this documentation with implementation details, pricing guidance, code examples, etc.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: ec994a02-c71a-8dea-8994-eb8c1e5e2992
* Version Independent ID: 2520c9c8-9d28-dd38-fa05-2c748b20ed8c
* Content: [Real-time Web Dashboard - Azure Solution Ideas](https://docs.microsoft.com/en-us/azure/architecture/solution-ideas/articles/real-time-web-dashboard)
* Content Source: [docs/solution-ideas/articles/real-time-web-dashboard.md](https://github.com/microsoftdocs/architecture-center/blob/master/docs/solution-ideas/articles/real-time-web-dashboard.md)
* Service: **architecture-center**
* Sub-service: **solution-idea**
* GitHub Login: @adamboeglin
* Microsoft Alias: **pnp** | non_priority | signalr realtime web dashboard it would be great if you can enhance this documentation with implementation details pricing guidance code examples etc document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service architecture center sub service solution idea github login adamboeglin microsoft alias pnp | 0 |
5,079 | 2,761,528,056 | IssuesEvent | 2015-04-28 17:42:54 | medic/medic-webapp | https://api.github.com/repos/medic/medic-webapp | closed | Cannot send a message to a contact | 3 - Acceptance testing Bug | I've plugged in a modem to test sending messages but get an error message after entering a contact and attempting to send a message.

| 1.0 | Cannot send a message to a contact - I've plugged in a modem to test sending messages but get an error message after entering a contact and attempting to send a message.

| non_priority | cannot send a message to a contact i ve plugged in a modem to test sending messages but get an error message after entering a contact and attempting to send a message | 0 |
78,131 | 22,150,844,596 | IssuesEvent | 2022-06-03 16:35:43 | apache/beam | https://api.github.com/repos/apache/beam | opened | Add commit SHA to artifact | P3 wish good first issue build-system | It would be useful to be able to identify commit SHA which is used to build an artifact. Looks like it's possible according to http://www.mojohaus.org/buildnumber-maven-plugin/usage.html
Imported from Jira [BEAM-2115](https://issues.apache.org/jira/browse/BEAM-2115). Original Jira may contain additional context.
Reported by: alexandreyc. | 1.0 | Add commit SHA to artifact - It would be useful to be able to identify commit SHA which is used to build an artifact. Looks like it's possible according to http://www.mojohaus.org/buildnumber-maven-plugin/usage.html
Imported from Jira [BEAM-2115](https://issues.apache.org/jira/browse/BEAM-2115). Original Jira may contain additional context.
Reported by: alexandreyc. | non_priority | add commit sha to artifact it would be useful to be able to identify commit sha which is used to build an artifact looks like it s possible according to imported from jira original jira may contain additional context reported by alexandreyc | 0 |
211,968 | 16,470,291,639 | IssuesEvent | 2021-05-23 09:11:54 | aws/aws-sdk-go-v2 | https://api.github.com/repos/aws/aws-sdk-go-v2 | opened | stscreds/assume_role_provider usage documentation is incorrect | documentation needs-triage | **Describe the issue with documentation**
When using the `stscreds.NewAssumeRoleProvider` for the first time, I looked at the examples in the source code which at time of writing shows:
```go
cfg, err := config.LoadDefaultConfig(context.TODO())
if err != nil {
log.Fatal(err)
}
stsSvc := sts.NewFromConfig(cfg)
creds := stscreds.NewAssumeRoleProvider(stsSvc, "myRoleArn")
cfg.Credentials = &aws.CredentialsCache{Provider: creds}
}
```
The issue is that, using `cfg.Credentials = &aws.CredentialsCache{Provider: creds}` doesn't compile. `aws.CredentialsCache` doesn't export the field `Provider`. If it once did, it is now a private field used by `aws.NewCredentialsCache`.
**To Reproduce (observed behavior)**
Follow the example code in the source file [here](https://github.com/aws/aws-sdk-go-v2/blob/36390a5d91d4e724cbed82fad2646dfe63487e3c/credentials/stscreds/assume_role_provider.go#L13)
**Expected behavior**
A working example of how to use `stscreds.NewAssumeRoleProvider`
**Additional information**
I was able to get my program working with:
```go
cfg, err := config.LoadDefaultConfig(context.TODO())
if err != nil {
log.Fatal(err)
}
stsSvc := sts.NewFromConfig(cfg)
creds := stscreds.NewAssumeRoleProvider(stsSvc, "myRoleArn")
cfg.Credentials = creds << assigning creds directly
```
I didn't want to raise a PR suggesting this as a fix because I'm not sure if this is the best way to do it, or if it's better to use a `CredentialsCache` in some way.
Sorry if this sounds nitpicky. Thanks for all the work on this SDK, I love using it ❤️ | 1.0 | stscreds/assume_role_provider usage documentation is incorrect - **Describe the issue with documentation**
When using the `stscreds.NewAssumeRoleProvider` for the first time, I looked at the examples in the source code which at time of writing shows:
```go
cfg, err := config.LoadDefaultConfig(context.TODO())
if err != nil {
log.Fatal(err)
}
stsSvc := sts.NewFromConfig(cfg)
creds := stscreds.NewAssumeRoleProvider(stsSvc, "myRoleArn")
cfg.Credentials = &aws.CredentialsCache{Provider: creds}
}
```
The issue is that, using `cfg.Credentials = &aws.CredentialsCache{Provider: creds}` doesn't compile. `aws.CredentialsCache` doesn't export the field `Provider`. If it once did, it is now a private field used by `aws.NewCredentialsCache`.
**To Reproduce (observed behavior)**
Follow the example code in the source file [here](https://github.com/aws/aws-sdk-go-v2/blob/36390a5d91d4e724cbed82fad2646dfe63487e3c/credentials/stscreds/assume_role_provider.go#L13)
**Expected behavior**
A working example of how to use `stscreds.NewAssumeRoleProvider`
**Additional information**
I was able to get my program working with:
```go
cfg, err := config.LoadDefaultConfig(context.TODO())
if err != nil {
log.Fatal(err)
}
stsSvc := sts.NewFromConfig(cfg)
creds := stscreds.NewAssumeRoleProvider(stsSvc, "myRoleArn")
cfg.Credentials = creds << assigning creds directly
```
I didn't want to raise a PR suggesting this as a fix because I'm not sure if this is the best way to do it, or if it's better to use a `CredentialsCache` in some way.
Sorry if this sounds nitpicky. Thanks for all the work on this SDK, I love using it ❤️ | non_priority | stscreds assume role provider usage documentation is incorrect describe the issue with documentation when using the stscreds newassumeroleprovider for the first time i looked at the examples in the source code which at time of writing shows go cfg err config loaddefaultconfig context todo if err nil log fatal err stssvc sts newfromconfig cfg creds stscreds newassumeroleprovider stssvc myrolearn cfg credentials aws credentialscache provider creds the issue is that using cfg credentials aws credentialscache provider creds doesn t compile aws credentialscache doesn t export the field provider if it once did it is now a private field used by aws newcredentialscache to reproduce observed behavior follow the example code in the source file expected behavior a working example of how to use stscreds newassumeroleprovider additional information i was able to get my program working with go cfg err config loaddefaultconfig context todo if err nil log fatal err stssvc sts newfromconfig cfg creds stscreds newassumeroleprovider stssvc myrolearn cfg credentials creds assigning creds directly i didn t want to raise a pr suggesting this as a fix because i m not sure if this is the best way to do it or if it s better to use a credentialscache in some way sorry if this sounds nitpicky thanks for all the work on this sdk i love using it ❤️ | 0 |
191,521 | 22,215,796,394 | IssuesEvent | 2022-06-08 01:24:33 | pustovitDmytro/base-api-client | https://api.github.com/repos/pustovitDmytro/base-api-client | closed | CVE-2022-1214 (High) detected in axios-0.21.4.tgz, axios-0.25.0.tgz - autoclosed | security vulnerability | ## CVE-2022-1214 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>axios-0.21.4.tgz</b>, <b>axios-0.25.0.tgz</b></p></summary>
<p>
<details><summary><b>axios-0.21.4.tgz</b></p></summary>
<p>Promise based HTTP client for the browser and node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/axios/-/axios-0.21.4.tgz">https://registry.npmjs.org/axios/-/axios-0.21.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/axios/package.json</p>
<p>
Dependency Hierarchy:
- semantic-release-telegram-1.5.1.tgz (Root Library)
- base-api-client-1.5.3.tgz
- :x: **axios-0.21.4.tgz** (Vulnerable Library)
</details>
<details><summary><b>axios-0.25.0.tgz</b></p></summary>
<p>Promise based HTTP client for the browser and node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/axios/-/axios-0.25.0.tgz">https://registry.npmjs.org/axios/-/axios-0.25.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/axios/package.json</p>
<p>
Dependency Hierarchy:
- :x: **axios-0.25.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/pustovitDmytro/base-api-client/commit/05e1fac43b1966bb4ea1c1c7974e0b61a93da69d">05e1fac43b1966bb4ea1c1c7974e0b61a93da69d</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Exposure of Sensitive Information to an Unauthorized Actor in GitHub repository axios/axios prior to 0.26.
<p>Publish Date: 2022-05-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-1214>CVE-2022-1214</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/ef7b4ab6-a3f6-4268-a21a-e7104d344607/">https://huntr.dev/bounties/ef7b4ab6-a3f6-4268-a21a-e7104d344607/</a></p>
<p>Release Date: 2022-05-03</p>
<p>Fix Resolution: 0.26.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-1214 (High) detected in axios-0.21.4.tgz, axios-0.25.0.tgz - autoclosed - ## CVE-2022-1214 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>axios-0.21.4.tgz</b>, <b>axios-0.25.0.tgz</b></p></summary>
<p>
<details><summary><b>axios-0.21.4.tgz</b></p></summary>
<p>Promise based HTTP client for the browser and node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/axios/-/axios-0.21.4.tgz">https://registry.npmjs.org/axios/-/axios-0.21.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/axios/package.json</p>
<p>
Dependency Hierarchy:
- semantic-release-telegram-1.5.1.tgz (Root Library)
- base-api-client-1.5.3.tgz
- :x: **axios-0.21.4.tgz** (Vulnerable Library)
</details>
<details><summary><b>axios-0.25.0.tgz</b></p></summary>
<p>Promise based HTTP client for the browser and node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/axios/-/axios-0.25.0.tgz">https://registry.npmjs.org/axios/-/axios-0.25.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/axios/package.json</p>
<p>
Dependency Hierarchy:
- :x: **axios-0.25.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/pustovitDmytro/base-api-client/commit/05e1fac43b1966bb4ea1c1c7974e0b61a93da69d">05e1fac43b1966bb4ea1c1c7974e0b61a93da69d</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Exposure of Sensitive Information to an Unauthorized Actor in GitHub repository axios/axios prior to 0.26.
<p>Publish Date: 2022-05-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-1214>CVE-2022-1214</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/ef7b4ab6-a3f6-4268-a21a-e7104d344607/">https://huntr.dev/bounties/ef7b4ab6-a3f6-4268-a21a-e7104d344607/</a></p>
<p>Release Date: 2022-05-03</p>
<p>Fix Resolution: 0.26.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in axios tgz axios tgz autoclosed cve high severity vulnerability vulnerable libraries axios tgz axios tgz axios tgz promise based http client for the browser and node js library home page a href path to dependency file package json path to vulnerable library node modules axios package json dependency hierarchy semantic release telegram tgz root library base api client tgz x axios tgz vulnerable library axios tgz promise based http client for the browser and node js library home page a href path to dependency file package json path to vulnerable library node modules axios package json dependency hierarchy x axios tgz vulnerable library found in head commit a href found in base branch master vulnerability details exposure of sensitive information to an unauthorized actor in github repository axios axios prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
79,017 | 22,591,494,368 | IssuesEvent | 2022-06-28 20:22:42 | golang/go | https://api.github.com/repos/golang/go | closed | x/build/env/linux-arm64/packet: restrict CPUs to a reasonable number of cores | Builders NeedsInvestigation | During the Go 1.14 beta1 release, we had a number of failures due to issues on our arm64 builders #36166.
Inspecting the build box, we discovered that our 96 core machine was very overloaded: a 1 minute load of over 300. This appeared to be related to the failures we encountered.
An initial fix of a maximum of 2 containers with 48 cores each seemed to resolve the issue, but there's likely a more efficient configuration. | 1.0 | x/build/env/linux-arm64/packet: restrict CPUs to a reasonable number of cores - During the Go 1.14 beta1 release, we had a number of failures due to issues on our arm64 builders #36166.
Inspecting the build box, we discovered that our 96 core machine was very overloaded: a 1 minute load of over 300. This appeared to be related to the failures we encountered.
An initial fix of a maximum of 2 containers with 48 cores each seemed to resolve the issue, but there's likely a more efficient configuration. | non_priority | x build env linux packet restrict cpus to a reasonable number of cores during the go release we had a number of failures due to issues on our builders inspecting the build box we discovered that our core machine was very overloaded a minute load of over this appeared to be related to the failures we encountered an initial fix of a maximum of containers with cores each seemed to resolve the issue but there s likely a more efficient configuration | 0 |
49,240 | 20,691,900,442 | IssuesEvent | 2022-03-11 01:44:42 | graphprotocol/indexer | https://api.github.com/repos/graphprotocol/indexer | opened | Do not hold onto receipts with 0 value | enhancement indexer-service | Towards resolving #278
The contracts do not support collecting receipts with 0 value, so let's disregard 0 value receipts early on instead of saving them. I'm expecting the update to take place in the [AllocationReceiptManager](https://github.com/graphprotocol/indexer/blob/main/packages/indexer-service/src/query-fees/allocations.ts#L82). | 1.0 | Do not hold onto receipts with 0 value - Towards resolving #278
The contracts do not support collecting receipts with 0 value, so let's disregard 0 value receipts early on instead of saving them. I'm expecting the update to take place in the [AllocationReceiptManager](https://github.com/graphprotocol/indexer/blob/main/packages/indexer-service/src/query-fees/allocations.ts#L82). | non_priority | do not hold onto receipts with value towards resolving the contracts do not support collecting receipts with value so let s disregard value receipts early on instead of saving them i m expecting the update to take place in the | 0 |
193,655 | 22,216,246,831 | IssuesEvent | 2022-06-08 02:10:44 | maddyCode23/linux-4.1.15 | https://api.github.com/repos/maddyCode23/linux-4.1.15 | reopened | CVE-2018-10938 (Medium) detected in linux-stable-rtv4.1.33 | security vulnerability | ## CVE-2018-10938 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/maddyCode23/linux-4.1.15/commit/f1f3d2b150be669390b32dfea28e773471bdd6e7">f1f3d2b150be669390b32dfea28e773471bdd6e7</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv4/cipso_ipv4.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv4/cipso_ipv4.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in the Linux kernel present since v4.0-rc1 and through v4.13-rc4. A crafted network packet sent remotely by an attacker may force the kernel to enter an infinite loop in the cipso_v4_optptr() function in net/ipv4/cipso_ipv4.c leading to a denial-of-service. A certain non-default configuration of LSM (Linux Security Module) and NetLabel should be set up on a system before an attacker could leverage this flaw.
<p>Publish Date: 2018-08-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-10938>CVE-2018-10938</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-10938">https://nvd.nist.gov/vuln/detail/CVE-2018-10938</a></p>
<p>Release Date: 2018-08-27</p>
<p>Fix Resolution: linux-yocto - 5.4.20+gitAUTOINC+c11911d4d1_f4d7dbafb1,4.8.26+gitAUTOINC+1c60e003c7_27efc3ba68</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-10938 (Medium) detected in linux-stable-rtv4.1.33 - ## CVE-2018-10938 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/maddyCode23/linux-4.1.15/commit/f1f3d2b150be669390b32dfea28e773471bdd6e7">f1f3d2b150be669390b32dfea28e773471bdd6e7</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv4/cipso_ipv4.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv4/cipso_ipv4.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in the Linux kernel present since v4.0-rc1 and through v4.13-rc4. A crafted network packet sent remotely by an attacker may force the kernel to enter an infinite loop in the cipso_v4_optptr() function in net/ipv4/cipso_ipv4.c leading to a denial-of-service. A certain non-default configuration of LSM (Linux Security Module) and NetLabel should be set up on a system before an attacker could leverage this flaw.
<p>Publish Date: 2018-08-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-10938>CVE-2018-10938</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-10938">https://nvd.nist.gov/vuln/detail/CVE-2018-10938</a></p>
<p>Release Date: 2018-08-27</p>
<p>Fix Resolution: linux-yocto - 5.4.20+gitAUTOINC+c11911d4d1_f4d7dbafb1,4.8.26+gitAUTOINC+1c60e003c7_27efc3ba68</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linux stable cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files net cipso c net cipso c vulnerability details a flaw was found in the linux kernel present since and through a crafted network packet sent remotely by an attacker may force the kernel to enter an infinite loop in the cipso optptr function in net cipso c leading to a denial of service a certain non default configuration of lsm linux security module and netlabel should be set up on a system before an attacker could leverage this flaw publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution linux yocto gitautoinc gitautoinc step up your open source security game with whitesource | 0 |
222,659 | 17,086,668,254 | IssuesEvent | 2021-07-08 12:44:13 | openkfw/TruBudget | https://api.github.com/repos/openkfw/TruBudget | closed | Developer-Setup.md outdated | documentation |
## Description 😯
With the addtion of DMS (minio) developer setup guide is out of date.
When trying to run TruBudget, according to the guide, developer ends up with application that is not working.
AFAK, at least minio module and envrionmental variables are missing.
## Steps to Reproduce 🕹
Steps:
1. Start TruBudget by the developer setup guide
2. 🚫
## Your Environment 🌎
| Tech | Version |
| -------------- | ------- |
| Frontend | v1.?.? |
| API | v1.?.? |
| Blockchain | v1.?.? |
| Export-Service | v1.?.? |
| Email-Service | v1.?.? |
| Chrome-Browser | ? |
| etc. | |
| 1.0 | Developer-Setup.md outdated -
## Description 😯
With the addtion of DMS (minio) developer setup guide is out of date.
When trying to run TruBudget, according to the guide, developer ends up with application that is not working.
AFAK, at least minio module and envrionmental variables are missing.
## Steps to Reproduce 🕹
Steps:
1. Start TruBudget by the developer setup guide
2. 🚫
## Your Environment 🌎
| Tech | Version |
| -------------- | ------- |
| Frontend | v1.?.? |
| API | v1.?.? |
| Blockchain | v1.?.? |
| Export-Service | v1.?.? |
| Email-Service | v1.?.? |
| Chrome-Browser | ? |
| etc. | |
| non_priority | developer setup md outdated description 😯 with the addtion of dms minio developer setup guide is out of date when trying to run trubudget according to the guide developer ends up with application that is not working afak at least minio module and envrionmental variables are missing steps to reproduce 🕹 steps start trubudget by the developer setup guide 🚫 your environment 🌎 tech version frontend api blockchain export service email service chrome browser etc | 0 |
40,986 | 5,328,671,739 | IssuesEvent | 2017-02-15 12:49:57 | Semantic-Org/Semantic-UI | https://api.github.com/repos/Semantic-Org/Semantic-UI | closed | onHide - return false not canceling the popup hide. | Needs Test Case | eg:
angular.element('.menu').popup({
on: 'click',
// scrollContext: '',
hoverable: true,
position: 'bottom left',
closable: true,
hideOnScroll: false,
delay: {
hide: 1000
},
onHide: function(ele) {
return false; // This is not canceling the popup from hide
}
}); | 1.0 | onHide - return false not canceling the popup hide. - eg:
angular.element('.menu').popup({
on: 'click',
// scrollContext: '',
hoverable: true,
position: 'bottom left',
closable: true,
hideOnScroll: false,
delay: {
hide: 1000
},
onHide: function(ele) {
return false; // This is not canceling the popup from hide
}
}); | non_priority | onhide return false not canceling the popup hide eg angular element menu popup on click scrollcontext hoverable true position bottom left closable true hideonscroll false delay hide onhide function ele return false this is not canceling the popup from hide | 0 |
191,745 | 15,302,862,687 | IssuesEvent | 2021-02-24 15:11:17 | open-jarvis/server | https://api.github.com/repos/open-jarvis/server | closed | IP configuration fails | documentation enhancement | ## Expected behaviour:
* IP configuration working on all os
## Actual behaviour:
* IP configuration only working on Raspbian
* Not working on systems which do not have the `/etc/dhcpcd.conf` file | 1.0 | IP configuration fails - ## Expected behaviour:
* IP configuration working on all os
## Actual behaviour:
* IP configuration only working on Raspbian
* Not working on systems which do not have the `/etc/dhcpcd.conf` file | non_priority | ip configuration fails expected behaviour ip configuration working on all os actual behaviour ip configuration only working on raspbian not working on systems which do not have the etc dhcpcd conf file | 0 |
2,871 | 5,233,994,471 | IssuesEvent | 2017-01-30 14:34:00 | ConnectWeather/LocalVisibility | https://api.github.com/repos/ConnectWeather/LocalVisibility | opened | Log in | Implementation Requirements | * The service should only be available for the client and their employees, secured from the outside.
* The client has requested that their email addresses can be used as a username. | 1.0 | Log in - * The service should only be available for the client and their employees, secured from the outside.
* The client has requested that their email addresses can be used as a username. | non_priority | log in the service should only be available for the client and their employees secured from the outside the client has requested that their email addresses can be used as a username | 0 |
128,426 | 18,048,209,562 | IssuesEvent | 2021-09-19 09:09:56 | jinhogate/pizza_angular | https://api.github.com/repos/jinhogate/pizza_angular | opened | CVE-2019-13173 (High) detected in fstream-1.0.11.tgz | security vulnerability | ## CVE-2019-13173 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>fstream-1.0.11.tgz</b></p></summary>
<p>Advanced file system stream things</p>
<p>Library home page: <a href="https://registry.npmjs.org/fstream/-/fstream-1.0.11.tgz">https://registry.npmjs.org/fstream/-/fstream-1.0.11.tgz</a></p>
<p>
Dependency Hierarchy:
- build-angular-0.6.8.tgz (Root Library)
- node-sass-4.9.3.tgz
- node-gyp-3.8.0.tgz
- :x: **fstream-1.0.11.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jinhogate/pizza_angular/commit/353ead6609cbe90c767728d4050746689c22c532">353ead6609cbe90c767728d4050746689c22c532</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
fstream before 1.0.12 is vulnerable to Arbitrary File Overwrite. Extracting tarballs containing a hardlink to a file that already exists in the system, and a file that matches the hardlink, will overwrite the system's file with the contents of the extracted file. The fstream.DirWriter() function is vulnerable.
<p>Publish Date: 2019-07-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-13173>CVE-2019-13173</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-13173">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-13173</a></p>
<p>Release Date: 2019-07-02</p>
<p>Fix Resolution: 1.0.12</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-13173 (High) detected in fstream-1.0.11.tgz - ## CVE-2019-13173 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>fstream-1.0.11.tgz</b></p></summary>
<p>Advanced file system stream things</p>
<p>Library home page: <a href="https://registry.npmjs.org/fstream/-/fstream-1.0.11.tgz">https://registry.npmjs.org/fstream/-/fstream-1.0.11.tgz</a></p>
<p>
Dependency Hierarchy:
- build-angular-0.6.8.tgz (Root Library)
- node-sass-4.9.3.tgz
- node-gyp-3.8.0.tgz
- :x: **fstream-1.0.11.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jinhogate/pizza_angular/commit/353ead6609cbe90c767728d4050746689c22c532">353ead6609cbe90c767728d4050746689c22c532</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
fstream before 1.0.12 is vulnerable to Arbitrary File Overwrite. Extracting tarballs containing a hardlink to a file that already exists in the system, and a file that matches the hardlink, will overwrite the system's file with the contents of the extracted file. The fstream.DirWriter() function is vulnerable.
<p>Publish Date: 2019-07-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-13173>CVE-2019-13173</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-13173">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-13173</a></p>
<p>Release Date: 2019-07-02</p>
<p>Fix Resolution: 1.0.12</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in fstream tgz cve high severity vulnerability vulnerable library fstream tgz advanced file system stream things library home page a href dependency hierarchy build angular tgz root library node sass tgz node gyp tgz x fstream tgz vulnerable library found in head commit a href found in base branch master vulnerability details fstream before is vulnerable to arbitrary file overwrite extracting tarballs containing a hardlink to a file that already exists in the system and a file that matches the hardlink will overwrite the system s file with the contents of the extracted file the fstream dirwriter function is vulnerable publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
68,886 | 21,942,082,101 | IssuesEvent | 2022-05-23 19:14:45 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | clicking permalinks for search results can result in permalinks being off the bottom of the page | T-Defect P2 S-Major A-Timeline | by quite a long way. i think this is a regression. although my window was quite large | 1.0 | clicking permalinks for search results can result in permalinks being off the bottom of the page - by quite a long way. i think this is a regression. although my window was quite large | non_priority | clicking permalinks for search results can result in permalinks being off the bottom of the page by quite a long way i think this is a regression although my window was quite large | 0 |
117,932 | 17,569,299,045 | IssuesEvent | 2021-08-14 10:41:16 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | opened | Vulnerability roundup 105: mosquitto-2.0.10: 2 advisories [7.5] | 1.severity: security | [search](https://search.nix.gsc.io/?q=mosquitto&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=mosquitto+in%3Apath&type=Code)
* [ ] [CVE-2021-34432](https://nvd.nist.gov/vuln/detail/CVE-2021-34432) CVSSv3=7.5 (nixos-21.05)
* [ ] [CVE-2021-34431](https://nvd.nist.gov/vuln/detail/CVE-2021-34431) CVSSv3=6.5 (nixos-21.05)
## CVE details
### CVE-2021-34432
In Eclipse Mosquitto versions 2.07 and earlier, the server will crash if the client tries to send a PUBLISH packet with topic length = 0.
### CVE-2021-34431
In Eclipse Mosquitto version 1.6 to 2.0.10, if an authenticated client that had connected with MQTT v5 sent a crafted CONNECT message to the broker a memory leak would occur, which could be used to provide a DoS attack against the broker.
-----
Scanned versions: nixos-21.05: ad6e733d633.
Cc @peterhoeg
| True | Vulnerability roundup 105: mosquitto-2.0.10: 2 advisories [7.5] - [search](https://search.nix.gsc.io/?q=mosquitto&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=mosquitto+in%3Apath&type=Code)
* [ ] [CVE-2021-34432](https://nvd.nist.gov/vuln/detail/CVE-2021-34432) CVSSv3=7.5 (nixos-21.05)
* [ ] [CVE-2021-34431](https://nvd.nist.gov/vuln/detail/CVE-2021-34431) CVSSv3=6.5 (nixos-21.05)
## CVE details
### CVE-2021-34432
In Eclipse Mosquitto versions 2.07 and earlier, the server will crash if the client tries to send a PUBLISH packet with topic length = 0.
### CVE-2021-34431
In Eclipse Mosquitto version 1.6 to 2.0.10, if an authenticated client that had connected with MQTT v5 sent a crafted CONNECT message to the broker a memory leak would occur, which could be used to provide a DoS attack against the broker.
-----
Scanned versions: nixos-21.05: ad6e733d633.
Cc @peterhoeg
| non_priority | vulnerability roundup mosquitto advisories nixos nixos cve details cve in eclipse mosquitto versions and earlier the server will crash if the client tries to send a publish packet with topic length cve in eclipse mosquitto version to if an authenticated client that had connected with mqtt sent a crafted connect message to the broker a memory leak would occur which could be used to provide a dos attack against the broker scanned versions nixos cc peterhoeg | 0 |
156,498 | 12,312,558,741 | IssuesEvent | 2020-05-12 14:06:13 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: kv0bench/nodes=10/cpu=8/shards=20/sequential failed | C-test-failure O-roachtest O-robot branch-master release-blocker | [(roachtest).kv0bench/nodes=10/cpu=8/shards=20/sequential failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=1930994&tab=buildLog) on [master@1d6db7e386e3ab21bca53f38637014f61153dc90](https://github.com/cockroachdb/cockroach/commits/1d6db7e386e3ab21bca53f38637014f61153dc90):
```
|
| stdout:
| 57357.5 1.5 10.5 16.3 33.6 write
| 294.0s 0 59967.1 57366.4 1.5 10.0 15.2 26.2 write
| 295.0s 0 59987.7 57375.3 1.5 10.0 15.7 44.0 write
| 296.0s 0 59953.2 57383.7 1.5 10.5 16.3 46.1 write
| 297.0s 0 59997.2 57392.8 1.6 11.0 18.9 41.9 write
| 298.0s 0 60254.5 57402.3 1.6 11.0 17.8 28.3 write
| 299.0s 0 60035.9 57411.2 1.6 13.1 22.0 35.7 write
| 300.0s 0 59755.9 57419.5 1.7 13.1 21.0 41.9 write
| _elapsed___errors__ops/sec(inst)___ops/sec(cum)__p50(ms)__p95(ms)__p99(ms)_pMax(ms)
| 1.0s 0 60065.8 60370.5 1.7 12.6 19.9 37.7 write
| 2.0s 0 59903.4 60134.7 1.7 13.1 21.0 39.8 write
| 3.0s 0 60051.6 60102.8 1.6 12.1 18.9 32.5 write
| 4.0s 0 60117.1 60106.5 1.6 10.5 16.3 29.4 write
| 5.0s 0 60124.9 60105.3 1.6 11.0 17.8 46.1 write
| 6.0s 0 59877.0 60078.3 1.6 11.5 17.8 35.7 write
| 7.0s 0 60149.0 60084.0 1.6 10.5 16.8 33.6 write
| 8.0s 0 60036.0 60075.6 1.5 11.0 17.8 32.5 write
| 9.0s 0 60027.5 60074.0 1.5 10.0 15.2 24.1 write
| 10.0s 0 59887.5 60050.2 1.5 10.0 15.7 31.5 write
| 11.0s 0 60265.2 60070.4 1.5 10.0 15.7 33.6 write
| 12.0s 0 60021.7 60067.5 1.5 10.5 16.3 39.8 write
| 13.0s 0 59889.4 60053.8 1.6 11.5 17.8 37.7 write
| 14.0s 0 60156.9 60063.3 1.6 11.0 17.8 39.8 write
| 15.0s 0 59841.3 60045.6 1.6 11.5 18.9 35.7 write
| 16.0s 0 59980.3 60045.5 1.7 12.1 19.9 31.5 write
| 17.0s 0 60272.8 60056.1 1.7 12.1 19.9 44.0 write
| 18.0s 0 60003.0 60055.2 1.6 13.1 21.0 39.8 write
| 19.0s 0 60105.5 60055.4 1.6 13.1 22.0 226.5 write
| 20.0s 0 60036.7 60054.4 1.6 12.1 19.9 39.8 write
| _elapsed___errors__ops/sec(inst)___ops/sec(cum)__p50(ms)__p95(ms)__p99(ms)_pMax(ms)
| 21.0s 0 60038.5 60052.6 1.6 11.0 16.8 29.4 write
| 22.0s 0 60148.3 60059.9 1.6 13.1 19.9 46.1 write
| 23.0s 0 59902.9 60051.7 1.6 11.5 18.9 37.7 write
| 24.0s 0 37084.0 59091.5 1.5 10.5 16.8 32.5 write
| 25.0s 0 0.0 56727.0 0.0 0.0 0.0 0.0 write
| 26.0s 0 0.0 54544.5 0.0 0.0 0.0 0.0 write
| 27.0s 0 0.0 52523.6 0.0 0.0 0.0 0.0 write
| 28.0s 0 0.0 50647.1 0.0 0.0 0.0 0.0 write
| 29.0s 0 0.0 48900.1 0.0 0.0 0.0 0.0 write
| 30.0s 0 0.0 47269.7 0.0 0.0 0.0 0.0 write
| 31.0s 0 0.0 45744.4 0.0 0.0 0.0 0.0 write
| 32.0s 0 0.0 44314.5 0.0 0.0 0.0 0.0 write
| 33.0s 0 0.0 42971.3 0.0 0.0 0.0 0.0 write
| 34.0s 0 0.0 41707.1 0.0 0.0 0.0 0.0 write
| 35.0s 0 0.0 40515.1 0.0 0.0 0.0 0.0 write
| 36.0s 0 0.0 39389.4 0.0 0.0 0.0 0.0 write
Wraps: (12) exit status 30
Error types: (1) *withstack.withStack (2) *errutil.withMessage (3) *withstack.withStack (4) *errutil.withMessage (5) *withstack.withStack (6) *safedetails.withSafeDetails (7) *errutil.withMessage (8) *withstack.withStack (9) *safedetails.withSafeDetails (10) *errutil.withMessage (11) *main.withCommandDetails (12) *exec.ExitError
```
<details><summary>More</summary><p>
Artifacts: [/kv0bench/nodes=10/cpu=8/shards=20/sequential](https://teamcity.cockroachdb.com/viewLog.html?buildId=1930994&tab=artifacts#/kv0bench/nodes=10/cpu=8/shards=20/sequential)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Akv0bench%2Fnodes%3D10%2Fcpu%3D8%2Fshards%3D20%2Fsequential.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| 2.0 | roachtest: kv0bench/nodes=10/cpu=8/shards=20/sequential failed - [(roachtest).kv0bench/nodes=10/cpu=8/shards=20/sequential failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=1930994&tab=buildLog) on [master@1d6db7e386e3ab21bca53f38637014f61153dc90](https://github.com/cockroachdb/cockroach/commits/1d6db7e386e3ab21bca53f38637014f61153dc90):
```
|
| stdout:
| 57357.5 1.5 10.5 16.3 33.6 write
| 294.0s 0 59967.1 57366.4 1.5 10.0 15.2 26.2 write
| 295.0s 0 59987.7 57375.3 1.5 10.0 15.7 44.0 write
| 296.0s 0 59953.2 57383.7 1.5 10.5 16.3 46.1 write
| 297.0s 0 59997.2 57392.8 1.6 11.0 18.9 41.9 write
| 298.0s 0 60254.5 57402.3 1.6 11.0 17.8 28.3 write
| 299.0s 0 60035.9 57411.2 1.6 13.1 22.0 35.7 write
| 300.0s 0 59755.9 57419.5 1.7 13.1 21.0 41.9 write
| _elapsed___errors__ops/sec(inst)___ops/sec(cum)__p50(ms)__p95(ms)__p99(ms)_pMax(ms)
| 1.0s 0 60065.8 60370.5 1.7 12.6 19.9 37.7 write
| 2.0s 0 59903.4 60134.7 1.7 13.1 21.0 39.8 write
| 3.0s 0 60051.6 60102.8 1.6 12.1 18.9 32.5 write
| 4.0s 0 60117.1 60106.5 1.6 10.5 16.3 29.4 write
| 5.0s 0 60124.9 60105.3 1.6 11.0 17.8 46.1 write
| 6.0s 0 59877.0 60078.3 1.6 11.5 17.8 35.7 write
| 7.0s 0 60149.0 60084.0 1.6 10.5 16.8 33.6 write
| 8.0s 0 60036.0 60075.6 1.5 11.0 17.8 32.5 write
| 9.0s 0 60027.5 60074.0 1.5 10.0 15.2 24.1 write
| 10.0s 0 59887.5 60050.2 1.5 10.0 15.7 31.5 write
| 11.0s 0 60265.2 60070.4 1.5 10.0 15.7 33.6 write
| 12.0s 0 60021.7 60067.5 1.5 10.5 16.3 39.8 write
| 13.0s 0 59889.4 60053.8 1.6 11.5 17.8 37.7 write
| 14.0s 0 60156.9 60063.3 1.6 11.0 17.8 39.8 write
| 15.0s 0 59841.3 60045.6 1.6 11.5 18.9 35.7 write
| 16.0s 0 59980.3 60045.5 1.7 12.1 19.9 31.5 write
| 17.0s 0 60272.8 60056.1 1.7 12.1 19.9 44.0 write
| 18.0s 0 60003.0 60055.2 1.6 13.1 21.0 39.8 write
| 19.0s 0 60105.5 60055.4 1.6 13.1 22.0 226.5 write
| 20.0s 0 60036.7 60054.4 1.6 12.1 19.9 39.8 write
| _elapsed___errors__ops/sec(inst)___ops/sec(cum)__p50(ms)__p95(ms)__p99(ms)_pMax(ms)
| 21.0s 0 60038.5 60052.6 1.6 11.0 16.8 29.4 write
| 22.0s 0 60148.3 60059.9 1.6 13.1 19.9 46.1 write
| 23.0s 0 59902.9 60051.7 1.6 11.5 18.9 37.7 write
| 24.0s 0 37084.0 59091.5 1.5 10.5 16.8 32.5 write
| 25.0s 0 0.0 56727.0 0.0 0.0 0.0 0.0 write
| 26.0s 0 0.0 54544.5 0.0 0.0 0.0 0.0 write
| 27.0s 0 0.0 52523.6 0.0 0.0 0.0 0.0 write
| 28.0s 0 0.0 50647.1 0.0 0.0 0.0 0.0 write
| 29.0s 0 0.0 48900.1 0.0 0.0 0.0 0.0 write
| 30.0s 0 0.0 47269.7 0.0 0.0 0.0 0.0 write
| 31.0s 0 0.0 45744.4 0.0 0.0 0.0 0.0 write
| 32.0s 0 0.0 44314.5 0.0 0.0 0.0 0.0 write
| 33.0s 0 0.0 42971.3 0.0 0.0 0.0 0.0 write
| 34.0s 0 0.0 41707.1 0.0 0.0 0.0 0.0 write
| 35.0s 0 0.0 40515.1 0.0 0.0 0.0 0.0 write
| 36.0s 0 0.0 39389.4 0.0 0.0 0.0 0.0 write
Wraps: (12) exit status 30
Error types: (1) *withstack.withStack (2) *errutil.withMessage (3) *withstack.withStack (4) *errutil.withMessage (5) *withstack.withStack (6) *safedetails.withSafeDetails (7) *errutil.withMessage (8) *withstack.withStack (9) *safedetails.withSafeDetails (10) *errutil.withMessage (11) *main.withCommandDetails (12) *exec.ExitError
```
<details><summary>More</summary><p>
Artifacts: [/kv0bench/nodes=10/cpu=8/shards=20/sequential](https://teamcity.cockroachdb.com/viewLog.html?buildId=1930994&tab=artifacts#/kv0bench/nodes=10/cpu=8/shards=20/sequential)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Akv0bench%2Fnodes%3D10%2Fcpu%3D8%2Fshards%3D20%2Fsequential.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| non_priority | roachtest nodes cpu shards sequential failed on stdout write write write write write write write write elapsed errors ops sec inst ops sec cum ms ms ms pmax ms write write write write write write write write write write write write write write write write write write write write elapsed errors ops sec inst ops sec cum ms ms ms pmax ms write write write write write write write write write write write write write write write write wraps exit status error types withstack withstack errutil withmessage withstack withstack errutil withmessage withstack withstack safedetails withsafedetails errutil withmessage withstack withstack safedetails withsafedetails errutil withmessage main withcommanddetails exec exiterror more artifacts powered by | 0 |
11,659 | 7,643,012,070 | IssuesEvent | 2018-05-08 11:12:42 | woocommerce/woocommerce | https://api.github.com/repos/woocommerce/woocommerce | closed | Cart / Session data and frontend includes loaded for API requests | Focus: Performance | <!-- This form is for reporting bugs and issues specific to the WooCommerce plugin. This is not a support portal. If you need technical support from a human being, please submit a ticket via the helpdesk instead: https://woocommerce.com/contact-us/ -->
<!-- Usage questions can also be directed to the public support forum here: https://wordpress.org/support/plugin/woocommerce, unless this is a question about a premium extension in which case you should use the helpdesk. -->
<!-- If you have a feature request, submit it to: http://ideas.woocommerce.com/forums/133476-woocommerce -->
<!-- If you are a developer who needs a new filter/hook raise a PR instead :) -->
<!-- Please be as descriptive as possible; issues lacking the below details, or for any other reason than to report a bug, may be closed without action. -->
## Prerequisites
<!-- MARK COMPLETED ITEMS WITH AN [x] -->
- [x] I have searched for similar issues in both open and closed tickets and cannot find a duplicate
- [x] The issue still exists against the latest `master` branch of WooCommerce on Github (this is **not** the same version as on WordPress.org!)
- [x] I have attempted to find the simplest possible steps to reproduce the issue
- [ ] I have included a failing test as a pull request (Optional)
## Steps to reproduce the issue
<!-- We need to be able to reproduce the bug in order to fix it so please be descriptive! -->
1. Make any request to REST API
2. Look at the execution of is_request( 'frontend' ) method defined in class-woocommerce.php
## Expected/actual behavior
When I follow those steps, I see that the method returns true.
I was expecting to see the method returning false, such that the places that call it don't have to execute unneeded and potentially expensive code on API requests (ex: loading cart and running calculate_totals)
## Isolating the problem
<!-- MARK COMPLETED ITEMS WITH AN [x] -->
- [x] This bug happens with only WooCommerce plugin active
- [x] This bug happens with a default WordPress theme active, or [Storefront](https://woocommerce.com/storefront/)
- [x] I can reproduce this bug consistently using the steps above | True | Cart / Session data and frontend includes loaded for API requests - <!-- This form is for reporting bugs and issues specific to the WooCommerce plugin. This is not a support portal. If you need technical support from a human being, please submit a ticket via the helpdesk instead: https://woocommerce.com/contact-us/ -->
<!-- Usage questions can also be directed to the public support forum here: https://wordpress.org/support/plugin/woocommerce, unless this is a question about a premium extension in which case you should use the helpdesk. -->
<!-- If you have a feature request, submit it to: http://ideas.woocommerce.com/forums/133476-woocommerce -->
<!-- If you are a developer who needs a new filter/hook raise a PR instead :) -->
<!-- Please be as descriptive as possible; issues lacking the below details, or for any other reason than to report a bug, may be closed without action. -->
## Prerequisites
<!-- MARK COMPLETED ITEMS WITH AN [x] -->
- [x] I have searched for similar issues in both open and closed tickets and cannot find a duplicate
- [x] The issue still exists against the latest `master` branch of WooCommerce on Github (this is **not** the same version as on WordPress.org!)
- [x] I have attempted to find the simplest possible steps to reproduce the issue
- [ ] I have included a failing test as a pull request (Optional)
## Steps to reproduce the issue
<!-- We need to be able to reproduce the bug in order to fix it so please be descriptive! -->
1. Make any request to REST API
2. Look at the execution of is_request( 'frontend' ) method defined in class-woocommerce.php
## Expected/actual behavior
When I follow those steps, I see that the method returns true.
I was expecting to see the method returning false, such that the places that call it don't have to execute unneeded and potentially expensive code on API requests (ex: loading cart and running calculate_totals)
## Isolating the problem
<!-- MARK COMPLETED ITEMS WITH AN [x] -->
- [x] This bug happens with only WooCommerce plugin active
- [x] This bug happens with a default WordPress theme active, or [Storefront](https://woocommerce.com/storefront/)
- [x] I can reproduce this bug consistently using the steps above | non_priority | cart session data and frontend includes loaded for api requests prerequisites i have searched for similar issues in both open and closed tickets and cannot find a duplicate the issue still exists against the latest master branch of woocommerce on github this is not the same version as on wordpress org i have attempted to find the simplest possible steps to reproduce the issue i have included a failing test as a pull request optional steps to reproduce the issue make any request to rest api look at the execution of is request frontend method defined in class woocommerce php expected actual behavior when i follow those steps i see that the method returns true i was expecting to see the method returning false such that the places that call it don t have to execute unneeded and potentially expensive code on api requests ex loading cart and running calculate totals isolating the problem this bug happens with only woocommerce plugin active this bug happens with a default wordpress theme active or i can reproduce this bug consistently using the steps above | 0 |
372,660 | 26,012,424,763 | IssuesEvent | 2022-12-21 04:01:11 | dagger/dagger | https://api.github.com/repos/dagger/dagger | closed | Ship SDK-aware docs | area/documentation | ## Overview
This issue tracks the work required to ship a new documentation site for Dagger, that is *SDK-aware*:
* Explains Dagger as an engine which can be programmed via different SDKs
* Incorporate docs for CUE SDK (rebranding of the "classic" dagger 0.2)
* Incorporate docs for Go SDK
* Allow for easy addition of more SDK docs in the coming weeks
Other requirements include:
* No broken URLs if possible
* Minimize tooling and maintenance complication
## Completion
This issue is complete when the new SDK-aware docs are **shipped** to devel.docs.dagger.io:
* Any Go developer can, if given the URL, access the Go SDK Docs somewhere under https://devel.docs.dagger.io
* Using the docs at that URL, and no other information, a Go developer can successfully develop and run their first Dagger pipeline in Go
**THIS ISSUE DOES NOT TRACK LAUNCHING**: do not include work that changes the contents of https://dagger.io
## PR tracker
PRs in flight:
* #3450
* #3451
* #3452
* https://github.com/dagger/dagger/pull/3454
## Task list
**Create new docs sites -**
- [x] Vikram will create the structure of the new doc plan above as a single PR for review. We will add pages once the PR is approved
Dagger Overview page on the main docs site -
- [x] Solomon owns the introduction
**Go SDK Site -**
- [ ] @kpenfound will work on Getting started guide updates
- [ ] Vikram will move over the current docs to new site
**CUE SDK site -**
- [ ] @jpadams will help migrate old Dagger docs in the new CUE SDK docs site
- [ ] NEED OWNER to choose and change the Dagger binary name
- [ ] FIXME all the technical work required to make the CUE docs match this discussion. For example, CLI updates - https://github.com/dagger/dagger/discussions/3432#discussioncomment-3917550 @samalba @gerhard need help here to coordinate the technical requirements and release requirements
## Architecture
```mermaid
graph TD;
tl["Top-level docs"]
go["Go SDK docs"]
cue["CUE SDK docs"]
tl --> go & cue
```
## Experience
### 1. Click on docs.dagger.io
Sees a single site that includes the following:
- Introduction to Dagger Overview Page and a sidebar
- FAQ
Sidebar has the following:
- Go SDK button to push to a Go SDK microsite with it's own sidebar
- CUE SDK button that pushes to old Dagger Docs that are relevant with it's own side bar
### 2. When clicking one of the SDKs in the sidebar:
- You go to SDK-specific docs site
- Search only shows you that specific SDK documentation
- There is a docs home button on the top of the sidebar to easily get back to the main docs site if you'd like.
| 1.0 | Ship SDK-aware docs - ## Overview
This issue tracks the work required to ship a new documentation site for Dagger, that is *SDK-aware*:
* Explains Dagger as an engine which can be programmed via different SDKs
* Incorporate docs for CUE SDK (rebranding of the "classic" dagger 0.2)
* Incorporate docs for Go SDK
* Allow for easy addition of more SDK docs in the coming weeks
Other requirements include:
* No broken URLs if possible
* Minimize tooling and maintenance complication
## Completion
This issue is complete when the new SDK-aware docs are **shipped** to devel.docs.dagger.io:
* Any Go developer can, if given the URL, access the Go SDK Docs somewhere under https://devel.docs.dagger.io
* Using the docs at that URL, and no other information, a Go developer can successfully develop and run their first Dagger pipeline in Go
**THIS ISSUE DOES NOT TRACK LAUNCHING**: do not include work that changes the contents of https://dagger.io
## PR tracker
PRs in flight:
* #3450
* #3451
* #3452
* https://github.com/dagger/dagger/pull/3454
## Task list
**Create new docs sites -**
- [x] Vikram will create the structure of the new doc plan above as a single PR for review. We will add pages once the PR is approved
Dagger Overview page on the main docs site -
- [x] Solomon owns the introduction
**Go SDK Site -**
- [ ] @kpenfound will work on Getting started guide updates
- [ ] Vikram will move over the current docs to new site
**CUE SDK site -**
- [ ] @jpadams will help migrate old Dagger docs in the new CUE SDK docs site
- [ ] NEED OWNER to choose and change the Dagger binary name
- [ ] FIXME all the technical work required to make the CUE docs match this discussion. For example, CLI updates - https://github.com/dagger/dagger/discussions/3432#discussioncomment-3917550 @samalba @gerhard need help here to coordinate the technical requirements and release requirements
## Architecture
```mermaid
graph TD;
tl["Top-level docs"]
go["Go SDK docs"]
cue["CUE SDK docs"]
tl --> go & cue
```
## Experience
### 1. Click on docs.dagger.io
Sees a single site that includes the following:
- Introduction to Dagger Overview Page and a sidebar
- FAQ
Sidebar has the following:
- Go SDK button to push to a Go SDK microsite with it's own sidebar
- CUE SDK button that pushes to old Dagger Docs that are relevant with it's own side bar
### 2. When clicking one of the SDKs in the sidebar:
- You go to SDK-specific docs site
- Search only shows you that specific SDK documentation
- There is a docs home button on the top of the sidebar to easily get back to the main docs site if you'd like.
| non_priority | ship sdk aware docs overview this issue tracks the work required to ship a new documentation site for dagger that is sdk aware explains dagger as an engine which can be programmed via different sdks incorporate docs for cue sdk rebranding of the classic dagger incorporate docs for go sdk allow for easy addition of more sdk docs in the coming weeks other requirements include no broken urls if possible minimize tooling and maintenance complication completion this issue is complete when the new sdk aware docs are shipped to devel docs dagger io any go developer can if given the url access the go sdk docs somewhere under using the docs at that url and no other information a go developer can successfully develop and run their first dagger pipeline in go this issue does not track launching do not include work that changes the contents of pr tracker prs in flight task list create new docs sites vikram will create the structure of the new doc plan above as a single pr for review we will add pages once the pr is approved dagger overview page on the main docs site solomon owns the introduction go sdk site kpenfound will work on getting started guide updates vikram will move over the current docs to new site cue sdk site jpadams will help migrate old dagger docs in the new cue sdk docs site need owner to choose and change the dagger binary name fixme all the technical work required to make the cue docs match this discussion for example cli updates samalba gerhard need help here to coordinate the technical requirements and release requirements architecture mermaid graph td tl go cue tl go cue experience click on docs dagger io sees a single site that includes the following introduction to dagger overview page and a sidebar faq sidebar has the following go sdk button to push to a go sdk microsite with it s own sidebar cue sdk button that pushes to old dagger docs that are relevant with it s own side bar when clicking one of the sdks in the sidebar you go to sdk specific docs site search only shows you that specific sdk documentation there is a docs home button on the top of the sidebar to easily get back to the main docs site if you d like | 0 |
66,973 | 8,989,630,300 | IssuesEvent | 2019-02-01 00:44:25 | GatorEducator/gatorgradle | https://api.github.com/repos/GatorEducator/gatorgradle | closed | Fix the semantic version of the plugin given in documentationn | documentation good-first-issue help-wanted | The documentation currently states the wrong semantic version number for the plugin. In fact, it uses a "beta" number that is no longer common for the deployments of the plugin. Can we please update this number? | 1.0 | Fix the semantic version of the plugin given in documentationn - The documentation currently states the wrong semantic version number for the plugin. In fact, it uses a "beta" number that is no longer common for the deployments of the plugin. Can we please update this number? | non_priority | fix the semantic version of the plugin given in documentationn the documentation currently states the wrong semantic version number for the plugin in fact it uses a beta number that is no longer common for the deployments of the plugin can we please update this number | 0 |
189,604 | 22,047,075,385 | IssuesEvent | 2022-05-30 03:50:34 | madhans23/linux-4.1.15 | https://api.github.com/repos/madhans23/linux-4.1.15 | closed | CVE-2016-9754 (High) detected in linux-stable-rtv4.1.33 - autoclosed | security vulnerability | ## CVE-2016-9754 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/madhans23/linux-4.1.15/commit/f9d19044b0eef1965f9bc412d7d9e579b74ec968">f9d19044b0eef1965f9bc412d7d9e579b74ec968</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The ring_buffer_resize function in kernel/trace/ring_buffer.c in the profiling subsystem in the Linux kernel before 4.6.1 mishandles certain integer calculations, which allows local users to gain privileges by writing to the /sys/kernel/debug/tracing/buffer_size_kb file.
<p>Publish Date: 2017-01-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-9754>CVE-2016-9754</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2016-9754">https://www.linuxkernelcves.com/cves/CVE-2016-9754</a></p>
<p>Release Date: 2017-01-05</p>
<p>Fix Resolution: v4.7-rc1,v3.12.61,v3.14.71,v3.16.37,v3.18.35,v4.1.26,v4.4.12,v4.5.6,v4.6.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2016-9754 (High) detected in linux-stable-rtv4.1.33 - autoclosed - ## CVE-2016-9754 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/madhans23/linux-4.1.15/commit/f9d19044b0eef1965f9bc412d7d9e579b74ec968">f9d19044b0eef1965f9bc412d7d9e579b74ec968</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The ring_buffer_resize function in kernel/trace/ring_buffer.c in the profiling subsystem in the Linux kernel before 4.6.1 mishandles certain integer calculations, which allows local users to gain privileges by writing to the /sys/kernel/debug/tracing/buffer_size_kb file.
<p>Publish Date: 2017-01-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-9754>CVE-2016-9754</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2016-9754">https://www.linuxkernelcves.com/cves/CVE-2016-9754</a></p>
<p>Release Date: 2017-01-05</p>
<p>Fix Resolution: v4.7-rc1,v3.12.61,v3.14.71,v3.16.37,v3.18.35,v4.1.26,v4.4.12,v4.5.6,v4.6.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linux stable autoclosed cve high severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files vulnerability details the ring buffer resize function in kernel trace ring buffer c in the profiling subsystem in the linux kernel before mishandles certain integer calculations which allows local users to gain privileges by writing to the sys kernel debug tracing buffer size kb file publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
24,360 | 6,537,318,765 | IssuesEvent | 2017-08-31 21:52:20 | dotnet/coreclr | https://api.github.com/repos/dotnet/coreclr | closed | [RyuJIT/arm32] Assertion failed '(call->IsTailCallViaHelper() ...' | arch-arm32 area-CodeGen bug | At morph.cpp Line: 15829
Example:
```
Assert failure(PID 11796 [0x00002e14], Thread: 11632 [0x2d70]): Assertion failed '(call->IsTailCallViaHelper() && (compCurBB->bbJumpKind == BBJ_THROW)) || (call->IsFastTailCall() && (compCurBB->bbJumpKind == BBJ_RETURN) && (compCurBB->bbFlags & BBF_HAS_JMP))' in 'JitTest.TestClass:Method0(ref):ref' (IL size 36) File: c:\gh\coreclr\src\jit\morph.cpp Line: 15829 Image: c:\brucefo\tests\Windows_NT.arm.Checked\Tests\Core_Root\CoreRun.exe
```
Tests with this assert:
```
JIT\Directed\coverage\oldtests\callipinvoke\callipinvoke.cmd
JIT\Directed\coverage\oldtests\Desktop\callipinvoke_il_d\callipinvoke_il_d.cmd
JIT\Directed\coverage\oldtests\Desktop\callipinvoke_il_r\callipinvoke_il_r.cmd
JIT\Directed\IL\mutualrecur-tailcall\MutualRecur-TailCall\MutualRecur-TailCall.cmd
JIT\Directed\IL\PInvokeTail\TailWinApi\TailWinApi.cmd
JIT\Directed\IL\Tailcall\jitTailcall1\jitTailcall1.cmd
JIT\Directed\IL\Tailcall\JitTailcall2\JitTailcall2.cmd
JIT\Directed\perffix\primitivevt\callconv3_il_d\callconv3_il_d.cmd
JIT\Directed\perffix\primitivevt\callconv3_il_r\callconv3_il_r.cmd
JIT\Directed\pinvoke\tail\tail.cmd
JIT\Directed\tailcall\tailcall\tailcall.cmd
JIT\Directed\zeroinit\tail\tail.cmd
JIT\IL_Conformance\Old\Base\tailcall\tailcall.cmd
JIT\jit64\mcc\interop\mcc_i06\mcc_i06.cmd
JIT\jit64\mcc\interop\mcc_i16\mcc_i16.cmd
JIT\jit64\mcc\interop\mcc_i86\mcc_i86.cmd
JIT\Methodical\Boxing\boxunbox\_il_dbgtailcall\_il_dbgtailcall.cmd
JIT\Methodical\Boxing\boxunbox\_il_reltailcall\_il_reltailcall.cmd
JIT\Methodical\Boxing\misc\_dbgtailjump_il\_dbgtailjump_il.cmd
JIT\Methodical\Boxing\misc\_dbgtypedref\_dbgtypedref.cmd
JIT\Methodical\Boxing\misc\_reltailjump_il\_reltailjump_il.cmd
JIT\Methodical\Boxing\misc\_reltypedref\_reltypedref.cmd
JIT\Methodical\Coverage\hole\hole.cmd
JIT\Methodical\flowgraph\dev10_bug679008\ehDescriptorPtrUpdate\ehDescriptorPtrUpdate.cmd
JIT\Methodical\flowgraph\dev10_bug679053\regionLive\regionLive.cmd
JIT\Methodical\Invoke\25params\25param1c_il_d\25param1c_il_d.cmd
JIT\Methodical\Invoke\25params\25param1c_il_r\25param1c_il_r.cmd
JIT\Methodical\Invoke\25params\25param2c_il_d\25param2c_il_d.cmd
JIT\Methodical\Invoke\25params\25param2c_il_r\25param2c_il_r.cmd
JIT\Methodical\Invoke\25params\25param3c_il_d\25param3c_il_d.cmd
JIT\Methodical\Invoke\25params\25param3c_il_r\25param3c_il_r.cmd
JIT\Methodical\Invoke\25params\25paramMixed_il_d\25paramMixed_il_d.cmd
JIT\Methodical\Invoke\25params\25paramMixed_il_r\25paramMixed_il_r.cmd
JIT\Methodical\Invoke\fptr\_il_dbgftn_t\_il_dbgftn_t.cmd
JIT\Methodical\Invoke\fptr\_il_dbginstftn_t\_il_dbginstftn_t.cmd
JIT\Methodical\Invoke\fptr\_il_dbgrecurse_tail_call\_il_dbgrecurse_tail_call.cmd
JIT\Methodical\Invoke\fptr\_il_dbgrecurse_tail_calli\_il_dbgrecurse_tail_calli.cmd
JIT\Methodical\Invoke\fptr\_il_dbgvalftn_t\_il_dbgvalftn_t.cmd
JIT\Methodical\Invoke\fptr\_il_dbgvirtftn_t\_il_dbgvirtftn_t.cmd
JIT\Methodical\Invoke\fptr\_il_relftn_t\_il_relftn_t.cmd
JIT\Methodical\Invoke\fptr\_il_relinstftn_t\_il_relinstftn_t.cmd
JIT\Methodical\Invoke\fptr\_il_relrecurse_tail_call\_il_relrecurse_tail_call.cmd
JIT\Methodical\Invoke\fptr\_il_relrecurse_tail_calli\_il_relrecurse_tail_calli.cmd
JIT\Methodical\Invoke\fptr\_il_relvalftn_t\_il_relvalftn_t.cmd
JIT\Methodical\Invoke\fptr\_il_relvirtftn_t\_il_relvirtftn_t.cmd
JIT\Methodical\Invoke\SEH\_il_dbgcatchfault_tail\_il_dbgcatchfault_tail.cmd
JIT\Methodical\Invoke\SEH\_il_dbgcatchfinally_tail\_il_dbgcatchfinally_tail.cmd
JIT\Methodical\Invoke\SEH\_il_relcatchfault_tail\_il_relcatchfault_tail.cmd
JIT\Methodical\Invoke\SEH\_il_relcatchfinally_tail\_il_relcatchfinally_tail.cmd
JIT\Methodical\nonvirtualcall\tailcall_d\tailcall_d.cmd
JIT\Methodical\nonvirtualcall\tailcall_r\tailcall_r.cmd
JIT\Methodical\refany\_il_dbgarray2\_il_dbgarray2.cmd
JIT\Methodical\refany\_il_dbgarray3\_il_dbgarray3.cmd
JIT\Methodical\refany\_il_dbgindcall\_il_dbgindcall.cmd
JIT\Methodical\refany\_il_relindcall\_il_relindcall.cmd
JIT\Methodical\tailcall\_il_dbgcompat_enum\_il_dbgcompat_enum.cmd
JIT\Methodical\tailcall\_il_dbgcompat_i4_u\_il_dbgcompat_i4_u.cmd
JIT\Methodical\tailcall\_il_dbgcompat_obj\_il_dbgcompat_obj.cmd
JIT\Methodical\tailcall\_il_dbgcompat_v\_il_dbgcompat_v.cmd
JIT\Methodical\tailcall\_il_dbgdeep_array\_il_dbgdeep_array.cmd
JIT\Methodical\tailcall\_il_dbgdeep_array_nz\_il_dbgdeep_array_nz.cmd
JIT\Methodical\tailcall\_il_dbgdeep_gc\_il_dbgdeep_gc.cmd
JIT\Methodical\tailcall\_il_dbgdeep_inst\_il_dbgdeep_inst.cmd
JIT\Methodical\tailcall\_il_dbgdeep_value\_il_dbgdeep_value.cmd
JIT\Methodical\tailcall\_il_dbgdeep_virt\_il_dbgdeep_virt.cmd
JIT\Methodical\tailcall\_il_dbggcval\_il_dbggcval.cmd
JIT\Methodical\tailcall\_il_dbggcval_nested\_il_dbggcval_nested.cmd
JIT\Methodical\tailcall\_il_dbggcval_sideeffect\_il_dbggcval_sideeffect.cmd
JIT\Methodical\tailcall\_il_dbgrecurse_ep\_il_dbgrecurse_ep.cmd
JIT\Methodical\tailcall\_il_dbgrecurse_ep_void\_il_dbgrecurse_ep_void.cmd
JIT\Methodical\tailcall\_il_dbgreference_i\_il_dbgreference_i.cmd
JIT\Methodical\tailcall\_il_dbgtest_2a\_il_dbgtest_2a.cmd
JIT\Methodical\tailcall\_il_dbgtest_2b\_il_dbgtest_2b.cmd
JIT\Methodical\tailcall\_il_dbgtest_2c\_il_dbgtest_2c.cmd
JIT\Methodical\tailcall\_il_dbgtest_implicit\_il_dbgtest_implicit.cmd
JIT\Methodical\tailcall\_il_dbgtest_mutual_rec\_il_dbgtest_mutual_rec.cmd
JIT\Methodical\tailcall\_il_dbgtest_switch\_il_dbgtest_switch.cmd
JIT\Methodical\tailcall\_il_dbgtest_virt\_il_dbgtest_virt.cmd
JIT\Methodical\tailcall\_il_dbgtest_void\_il_dbgtest_void.cmd
JIT\Methodical\tailcall\_il_relcompat_enum\_il_relcompat_enum.cmd
JIT\Methodical\tailcall\_il_relcompat_i4_u\_il_relcompat_i4_u.cmd
JIT\Methodical\tailcall\_il_relcompat_obj\_il_relcompat_obj.cmd
JIT\Methodical\tailcall\_il_relcompat_v\_il_relcompat_v.cmd
JIT\Methodical\tailcall\_il_reldeep_array\_il_reldeep_array.cmd
JIT\Methodical\tailcall\_il_reldeep_array_nz\_il_reldeep_array_nz.cmd
JIT\Methodical\tailcall\_il_reldeep_gc\_il_reldeep_gc.cmd
JIT\Methodical\tailcall\_il_reldeep_inst\_il_reldeep_inst.cmd
JIT\Methodical\tailcall\_il_reldeep_value\_il_reldeep_value.cmd
JIT\Methodical\tailcall\_il_reldeep_virt\_il_reldeep_virt.cmd
JIT\Methodical\tailcall\_il_relgcval\_il_relgcval.cmd
JIT\Methodical\tailcall\_il_relgcval_nested\_il_relgcval_nested.cmd
JIT\Methodical\tailcall\_il_relgcval_sideeffect\_il_relgcval_sideeffect.cmd
JIT\Methodical\tailcall\_il_relrecurse_ep\_il_relrecurse_ep.cmd
JIT\Methodical\tailcall\_il_relrecurse_ep_void\_il_relrecurse_ep_void.cmd
JIT\Methodical\tailcall\_il_relreference_i\_il_relreference_i.cmd
JIT\Methodical\tailcall\_il_reltest_2a\_il_reltest_2a.cmd
JIT\Methodical\tailcall\_il_reltest_2b\_il_reltest_2b.cmd
JIT\Methodical\tailcall\_il_reltest_2c\_il_reltest_2c.cmd
JIT\Methodical\tailcall\_il_reltest_implicit\_il_reltest_implicit.cmd
JIT\Methodical\tailcall\_il_reltest_mutual_rec\_il_reltest_mutual_rec.cmd
JIT\Methodical\tailcall\_il_reltest_switch\_il_reltest_switch.cmd
JIT\Methodical\tailcall\_il_reltest_virt\_il_reltest_virt.cmd
JIT\Methodical\tailcall\_il_reltest_void\_il_reltest_void.cmd
JIT\Methodical\tailcall_v4\delegatetail\delegatetail.cmd
JIT\Methodical\tailcall_v4\tailcall_AV\tailcall_AV.cmd
JIT\Methodical\VT\callconv\_il_dbgjumps2\_il_dbgjumps2.cmd
JIT\Methodical\VT\callconv\_il_dbgjumps3\_il_dbgjumps3.cmd
JIT\Methodical\VT\callconv\_il_dbgjumps4\_il_dbgjumps4.cmd
JIT\Methodical\VT\callconv\_il_dbgvtret\_il_dbgvtret.cmd
JIT\Methodical\VT\callconv\_il_dbgvtret2\_il_dbgvtret2.cmd
JIT\Methodical\VT\callconv\_il_reljumps2\_il_reljumps2.cmd
JIT\Methodical\VT\callconv\_il_reljumps3\_il_reljumps3.cmd
JIT\Methodical\VT\callconv\_il_reljumps4\_il_reljumps4.cmd
JIT\Methodical\VT\callconv\_il_relvtret\_il_relvtret.cmd
JIT\Methodical\VT\callconv\_il_relvtret2\_il_relvtret2.cmd
JIT\opt\ETW\TailCallCases\TailCallCases.cmd
JIT\Regression\CLR-x86-JIT\V1-M09.5-PDC\b10894\b10894\b10894.cmd
JIT\Regression\CLR-x86-JIT\V1-M09.5-PDC\b26957\b26957\b26957.cmd
JIT\Regression\CLR-x86-JIT\V1-M10\b02043\b02043\b02043.cmd
JIT\Regression\CLR-x86-JIT\V1.2-M01\b06020\b06020\b06020.cmd
JIT\Regression\JitBlue\devdiv_902271\DevDiv_902271\DevDiv_902271.cmd
JIT\Regression\JitBlue\GitHub_5164\GitHub_5164\GitHub_5164.cmd
JIT\Regression\VS-ia64-JIT\M00\b84586\b84586\b84586.cmd
JIT\Regression\VS-ia64-JIT\V1.2-M02\b102518\b102518\b102518.cmd
JIT\Regression\VS-ia64-JIT\V1.2-M02\b102844\b102844\b102844.cmd
JIT\Regression\VS-ia64-JIT\V1.2-M02\b14364\b14364\b14364.cmd
JIT\Regression\VS-ia64-JIT\V1.2-M02\b17023\b17023\b17023.cmd
JIT\Regression\VS-ia64-JIT\V1.2-M02\b17904\b17904\b17904.cmd
JIT\Regression\VS-ia64-JIT\V2.0-Beta2\b356258\b356258\b356258.cmd
``` | 1.0 | [RyuJIT/arm32] Assertion failed '(call->IsTailCallViaHelper() ...' - At morph.cpp Line: 15829
Example:
```
Assert failure(PID 11796 [0x00002e14], Thread: 11632 [0x2d70]): Assertion failed '(call->IsTailCallViaHelper() && (compCurBB->bbJumpKind == BBJ_THROW)) || (call->IsFastTailCall() && (compCurBB->bbJumpKind == BBJ_RETURN) && (compCurBB->bbFlags & BBF_HAS_JMP))' in 'JitTest.TestClass:Method0(ref):ref' (IL size 36) File: c:\gh\coreclr\src\jit\morph.cpp Line: 15829 Image: c:\brucefo\tests\Windows_NT.arm.Checked\Tests\Core_Root\CoreRun.exe
```
Tests with this assert:
```
JIT\Directed\coverage\oldtests\callipinvoke\callipinvoke.cmd
JIT\Directed\coverage\oldtests\Desktop\callipinvoke_il_d\callipinvoke_il_d.cmd
JIT\Directed\coverage\oldtests\Desktop\callipinvoke_il_r\callipinvoke_il_r.cmd
JIT\Directed\IL\mutualrecur-tailcall\MutualRecur-TailCall\MutualRecur-TailCall.cmd
JIT\Directed\IL\PInvokeTail\TailWinApi\TailWinApi.cmd
JIT\Directed\IL\Tailcall\jitTailcall1\jitTailcall1.cmd
JIT\Directed\IL\Tailcall\JitTailcall2\JitTailcall2.cmd
JIT\Directed\perffix\primitivevt\callconv3_il_d\callconv3_il_d.cmd
JIT\Directed\perffix\primitivevt\callconv3_il_r\callconv3_il_r.cmd
JIT\Directed\pinvoke\tail\tail.cmd
JIT\Directed\tailcall\tailcall\tailcall.cmd
JIT\Directed\zeroinit\tail\tail.cmd
JIT\IL_Conformance\Old\Base\tailcall\tailcall.cmd
JIT\jit64\mcc\interop\mcc_i06\mcc_i06.cmd
JIT\jit64\mcc\interop\mcc_i16\mcc_i16.cmd
JIT\jit64\mcc\interop\mcc_i86\mcc_i86.cmd
JIT\Methodical\Boxing\boxunbox\_il_dbgtailcall\_il_dbgtailcall.cmd
JIT\Methodical\Boxing\boxunbox\_il_reltailcall\_il_reltailcall.cmd
JIT\Methodical\Boxing\misc\_dbgtailjump_il\_dbgtailjump_il.cmd
JIT\Methodical\Boxing\misc\_dbgtypedref\_dbgtypedref.cmd
JIT\Methodical\Boxing\misc\_reltailjump_il\_reltailjump_il.cmd
JIT\Methodical\Boxing\misc\_reltypedref\_reltypedref.cmd
JIT\Methodical\Coverage\hole\hole.cmd
JIT\Methodical\flowgraph\dev10_bug679008\ehDescriptorPtrUpdate\ehDescriptorPtrUpdate.cmd
JIT\Methodical\flowgraph\dev10_bug679053\regionLive\regionLive.cmd
JIT\Methodical\Invoke\25params\25param1c_il_d\25param1c_il_d.cmd
JIT\Methodical\Invoke\25params\25param1c_il_r\25param1c_il_r.cmd
JIT\Methodical\Invoke\25params\25param2c_il_d\25param2c_il_d.cmd
JIT\Methodical\Invoke\25params\25param2c_il_r\25param2c_il_r.cmd
JIT\Methodical\Invoke\25params\25param3c_il_d\25param3c_il_d.cmd
JIT\Methodical\Invoke\25params\25param3c_il_r\25param3c_il_r.cmd
JIT\Methodical\Invoke\25params\25paramMixed_il_d\25paramMixed_il_d.cmd
JIT\Methodical\Invoke\25params\25paramMixed_il_r\25paramMixed_il_r.cmd
JIT\Methodical\Invoke\fptr\_il_dbgftn_t\_il_dbgftn_t.cmd
JIT\Methodical\Invoke\fptr\_il_dbginstftn_t\_il_dbginstftn_t.cmd
JIT\Methodical\Invoke\fptr\_il_dbgrecurse_tail_call\_il_dbgrecurse_tail_call.cmd
JIT\Methodical\Invoke\fptr\_il_dbgrecurse_tail_calli\_il_dbgrecurse_tail_calli.cmd
JIT\Methodical\Invoke\fptr\_il_dbgvalftn_t\_il_dbgvalftn_t.cmd
JIT\Methodical\Invoke\fptr\_il_dbgvirtftn_t\_il_dbgvirtftn_t.cmd
JIT\Methodical\Invoke\fptr\_il_relftn_t\_il_relftn_t.cmd
JIT\Methodical\Invoke\fptr\_il_relinstftn_t\_il_relinstftn_t.cmd
JIT\Methodical\Invoke\fptr\_il_relrecurse_tail_call\_il_relrecurse_tail_call.cmd
JIT\Methodical\Invoke\fptr\_il_relrecurse_tail_calli\_il_relrecurse_tail_calli.cmd
JIT\Methodical\Invoke\fptr\_il_relvalftn_t\_il_relvalftn_t.cmd
JIT\Methodical\Invoke\fptr\_il_relvirtftn_t\_il_relvirtftn_t.cmd
JIT\Methodical\Invoke\SEH\_il_dbgcatchfault_tail\_il_dbgcatchfault_tail.cmd
JIT\Methodical\Invoke\SEH\_il_dbgcatchfinally_tail\_il_dbgcatchfinally_tail.cmd
JIT\Methodical\Invoke\SEH\_il_relcatchfault_tail\_il_relcatchfault_tail.cmd
JIT\Methodical\Invoke\SEH\_il_relcatchfinally_tail\_il_relcatchfinally_tail.cmd
JIT\Methodical\nonvirtualcall\tailcall_d\tailcall_d.cmd
JIT\Methodical\nonvirtualcall\tailcall_r\tailcall_r.cmd
JIT\Methodical\refany\_il_dbgarray2\_il_dbgarray2.cmd
JIT\Methodical\refany\_il_dbgarray3\_il_dbgarray3.cmd
JIT\Methodical\refany\_il_dbgindcall\_il_dbgindcall.cmd
JIT\Methodical\refany\_il_relindcall\_il_relindcall.cmd
JIT\Methodical\tailcall\_il_dbgcompat_enum\_il_dbgcompat_enum.cmd
JIT\Methodical\tailcall\_il_dbgcompat_i4_u\_il_dbgcompat_i4_u.cmd
JIT\Methodical\tailcall\_il_dbgcompat_obj\_il_dbgcompat_obj.cmd
JIT\Methodical\tailcall\_il_dbgcompat_v\_il_dbgcompat_v.cmd
JIT\Methodical\tailcall\_il_dbgdeep_array\_il_dbgdeep_array.cmd
JIT\Methodical\tailcall\_il_dbgdeep_array_nz\_il_dbgdeep_array_nz.cmd
JIT\Methodical\tailcall\_il_dbgdeep_gc\_il_dbgdeep_gc.cmd
JIT\Methodical\tailcall\_il_dbgdeep_inst\_il_dbgdeep_inst.cmd
JIT\Methodical\tailcall\_il_dbgdeep_value\_il_dbgdeep_value.cmd
JIT\Methodical\tailcall\_il_dbgdeep_virt\_il_dbgdeep_virt.cmd
JIT\Methodical\tailcall\_il_dbggcval\_il_dbggcval.cmd
JIT\Methodical\tailcall\_il_dbggcval_nested\_il_dbggcval_nested.cmd
JIT\Methodical\tailcall\_il_dbggcval_sideeffect\_il_dbggcval_sideeffect.cmd
JIT\Methodical\tailcall\_il_dbgrecurse_ep\_il_dbgrecurse_ep.cmd
JIT\Methodical\tailcall\_il_dbgrecurse_ep_void\_il_dbgrecurse_ep_void.cmd
JIT\Methodical\tailcall\_il_dbgreference_i\_il_dbgreference_i.cmd
JIT\Methodical\tailcall\_il_dbgtest_2a\_il_dbgtest_2a.cmd
JIT\Methodical\tailcall\_il_dbgtest_2b\_il_dbgtest_2b.cmd
JIT\Methodical\tailcall\_il_dbgtest_2c\_il_dbgtest_2c.cmd
JIT\Methodical\tailcall\_il_dbgtest_implicit\_il_dbgtest_implicit.cmd
JIT\Methodical\tailcall\_il_dbgtest_mutual_rec\_il_dbgtest_mutual_rec.cmd
JIT\Methodical\tailcall\_il_dbgtest_switch\_il_dbgtest_switch.cmd
JIT\Methodical\tailcall\_il_dbgtest_virt\_il_dbgtest_virt.cmd
JIT\Methodical\tailcall\_il_dbgtest_void\_il_dbgtest_void.cmd
JIT\Methodical\tailcall\_il_relcompat_enum\_il_relcompat_enum.cmd
JIT\Methodical\tailcall\_il_relcompat_i4_u\_il_relcompat_i4_u.cmd
JIT\Methodical\tailcall\_il_relcompat_obj\_il_relcompat_obj.cmd
JIT\Methodical\tailcall\_il_relcompat_v\_il_relcompat_v.cmd
JIT\Methodical\tailcall\_il_reldeep_array\_il_reldeep_array.cmd
JIT\Methodical\tailcall\_il_reldeep_array_nz\_il_reldeep_array_nz.cmd
JIT\Methodical\tailcall\_il_reldeep_gc\_il_reldeep_gc.cmd
JIT\Methodical\tailcall\_il_reldeep_inst\_il_reldeep_inst.cmd
JIT\Methodical\tailcall\_il_reldeep_value\_il_reldeep_value.cmd
JIT\Methodical\tailcall\_il_reldeep_virt\_il_reldeep_virt.cmd
JIT\Methodical\tailcall\_il_relgcval\_il_relgcval.cmd
JIT\Methodical\tailcall\_il_relgcval_nested\_il_relgcval_nested.cmd
JIT\Methodical\tailcall\_il_relgcval_sideeffect\_il_relgcval_sideeffect.cmd
JIT\Methodical\tailcall\_il_relrecurse_ep\_il_relrecurse_ep.cmd
JIT\Methodical\tailcall\_il_relrecurse_ep_void\_il_relrecurse_ep_void.cmd
JIT\Methodical\tailcall\_il_relreference_i\_il_relreference_i.cmd
JIT\Methodical\tailcall\_il_reltest_2a\_il_reltest_2a.cmd
JIT\Methodical\tailcall\_il_reltest_2b\_il_reltest_2b.cmd
JIT\Methodical\tailcall\_il_reltest_2c\_il_reltest_2c.cmd
JIT\Methodical\tailcall\_il_reltest_implicit\_il_reltest_implicit.cmd
JIT\Methodical\tailcall\_il_reltest_mutual_rec\_il_reltest_mutual_rec.cmd
JIT\Methodical\tailcall\_il_reltest_switch\_il_reltest_switch.cmd
JIT\Methodical\tailcall\_il_reltest_virt\_il_reltest_virt.cmd
JIT\Methodical\tailcall\_il_reltest_void\_il_reltest_void.cmd
JIT\Methodical\tailcall_v4\delegatetail\delegatetail.cmd
JIT\Methodical\tailcall_v4\tailcall_AV\tailcall_AV.cmd
JIT\Methodical\VT\callconv\_il_dbgjumps2\_il_dbgjumps2.cmd
JIT\Methodical\VT\callconv\_il_dbgjumps3\_il_dbgjumps3.cmd
JIT\Methodical\VT\callconv\_il_dbgjumps4\_il_dbgjumps4.cmd
JIT\Methodical\VT\callconv\_il_dbgvtret\_il_dbgvtret.cmd
JIT\Methodical\VT\callconv\_il_dbgvtret2\_il_dbgvtret2.cmd
JIT\Methodical\VT\callconv\_il_reljumps2\_il_reljumps2.cmd
JIT\Methodical\VT\callconv\_il_reljumps3\_il_reljumps3.cmd
JIT\Methodical\VT\callconv\_il_reljumps4\_il_reljumps4.cmd
JIT\Methodical\VT\callconv\_il_relvtret\_il_relvtret.cmd
JIT\Methodical\VT\callconv\_il_relvtret2\_il_relvtret2.cmd
JIT\opt\ETW\TailCallCases\TailCallCases.cmd
JIT\Regression\CLR-x86-JIT\V1-M09.5-PDC\b10894\b10894\b10894.cmd
JIT\Regression\CLR-x86-JIT\V1-M09.5-PDC\b26957\b26957\b26957.cmd
JIT\Regression\CLR-x86-JIT\V1-M10\b02043\b02043\b02043.cmd
JIT\Regression\CLR-x86-JIT\V1.2-M01\b06020\b06020\b06020.cmd
JIT\Regression\JitBlue\devdiv_902271\DevDiv_902271\DevDiv_902271.cmd
JIT\Regression\JitBlue\GitHub_5164\GitHub_5164\GitHub_5164.cmd
JIT\Regression\VS-ia64-JIT\M00\b84586\b84586\b84586.cmd
JIT\Regression\VS-ia64-JIT\V1.2-M02\b102518\b102518\b102518.cmd
JIT\Regression\VS-ia64-JIT\V1.2-M02\b102844\b102844\b102844.cmd
JIT\Regression\VS-ia64-JIT\V1.2-M02\b14364\b14364\b14364.cmd
JIT\Regression\VS-ia64-JIT\V1.2-M02\b17023\b17023\b17023.cmd
JIT\Regression\VS-ia64-JIT\V1.2-M02\b17904\b17904\b17904.cmd
JIT\Regression\VS-ia64-JIT\V2.0-Beta2\b356258\b356258\b356258.cmd
``` | non_priority | assertion failed call istailcallviahelper at morph cpp line example assert failure pid thread assertion failed call istailcallviahelper compcurbb bbjumpkind bbj throw call isfasttailcall compcurbb bbjumpkind bbj return compcurbb bbflags bbf has jmp in jittest testclass ref ref il size file c gh coreclr src jit morph cpp line image c brucefo tests windows nt arm checked tests core root corerun exe tests with this assert jit directed coverage oldtests callipinvoke callipinvoke cmd jit directed coverage oldtests desktop callipinvoke il d callipinvoke il d cmd jit directed coverage oldtests desktop callipinvoke il r callipinvoke il r cmd jit directed il mutualrecur tailcall mutualrecur tailcall mutualrecur tailcall cmd jit directed il pinvoketail tailwinapi tailwinapi cmd jit directed il tailcall cmd jit directed il tailcall cmd jit directed perffix primitivevt il d il d cmd jit directed perffix primitivevt il r il r cmd jit directed pinvoke tail tail cmd jit directed tailcall tailcall tailcall cmd jit directed zeroinit tail tail cmd jit il conformance old base tailcall tailcall cmd jit mcc interop mcc mcc cmd jit mcc interop mcc mcc cmd jit mcc interop mcc mcc cmd jit methodical boxing boxunbox il dbgtailcall il dbgtailcall cmd jit methodical boxing boxunbox il reltailcall il reltailcall cmd jit methodical boxing misc dbgtailjump il dbgtailjump il cmd jit methodical boxing misc dbgtypedref dbgtypedref cmd jit methodical boxing misc reltailjump il reltailjump il cmd jit methodical boxing misc reltypedref reltypedref cmd jit methodical coverage hole hole cmd jit methodical flowgraph ehdescriptorptrupdate ehdescriptorptrupdate cmd jit methodical flowgraph regionlive regionlive cmd jit methodical invoke il d il d cmd jit methodical invoke il r il r cmd jit methodical invoke il d il d cmd jit methodical invoke il r il r cmd jit methodical invoke il d il d cmd jit methodical invoke il r il r cmd jit methodical invoke il d il d cmd jit methodical invoke il r il r cmd jit methodical invoke fptr il dbgftn t il dbgftn t cmd jit methodical invoke fptr il dbginstftn t il dbginstftn t cmd jit methodical invoke fptr il dbgrecurse tail call il dbgrecurse tail call cmd jit methodical invoke fptr il dbgrecurse tail calli il dbgrecurse tail calli cmd jit methodical invoke fptr il dbgvalftn t il dbgvalftn t cmd jit methodical invoke fptr il dbgvirtftn t il dbgvirtftn t cmd jit methodical invoke fptr il relftn t il relftn t cmd jit methodical invoke fptr il relinstftn t il relinstftn t cmd jit methodical invoke fptr il relrecurse tail call il relrecurse tail call cmd jit methodical invoke fptr il relrecurse tail calli il relrecurse tail calli cmd jit methodical invoke fptr il relvalftn t il relvalftn t cmd jit methodical invoke fptr il relvirtftn t il relvirtftn t cmd jit methodical invoke seh il dbgcatchfault tail il dbgcatchfault tail cmd jit methodical invoke seh il dbgcatchfinally tail il dbgcatchfinally tail cmd jit methodical invoke seh il relcatchfault tail il relcatchfault tail cmd jit methodical invoke seh il relcatchfinally tail il relcatchfinally tail cmd jit methodical nonvirtualcall tailcall d tailcall d cmd jit methodical nonvirtualcall tailcall r tailcall r cmd jit methodical refany il il cmd jit methodical refany il il cmd jit methodical refany il dbgindcall il dbgindcall cmd jit methodical refany il relindcall il relindcall cmd jit methodical tailcall il dbgcompat enum il dbgcompat enum cmd jit methodical tailcall il dbgcompat u il dbgcompat u cmd jit methodical tailcall il dbgcompat obj il dbgcompat obj cmd jit methodical tailcall il dbgcompat v il dbgcompat v cmd jit methodical tailcall il dbgdeep array il dbgdeep array cmd jit methodical tailcall il dbgdeep array nz il dbgdeep array nz cmd jit methodical tailcall il dbgdeep gc il dbgdeep gc cmd jit methodical tailcall il dbgdeep inst il dbgdeep inst cmd jit methodical tailcall il dbgdeep value il dbgdeep value cmd jit methodical tailcall il dbgdeep virt il dbgdeep virt cmd jit methodical tailcall il dbggcval il dbggcval cmd jit methodical tailcall il dbggcval nested il dbggcval nested cmd jit methodical tailcall il dbggcval sideeffect il dbggcval sideeffect cmd jit methodical tailcall il dbgrecurse ep il dbgrecurse ep cmd jit methodical tailcall il dbgrecurse ep void il dbgrecurse ep void cmd jit methodical tailcall il dbgreference i il dbgreference i cmd jit methodical tailcall il dbgtest il dbgtest cmd jit methodical tailcall il dbgtest il dbgtest cmd jit methodical tailcall il dbgtest il dbgtest cmd jit methodical tailcall il dbgtest implicit il dbgtest implicit cmd jit methodical tailcall il dbgtest mutual rec il dbgtest mutual rec cmd jit methodical tailcall il dbgtest switch il dbgtest switch cmd jit methodical tailcall il dbgtest virt il dbgtest virt cmd jit methodical tailcall il dbgtest void il dbgtest void cmd jit methodical tailcall il relcompat enum il relcompat enum cmd jit methodical tailcall il relcompat u il relcompat u cmd jit methodical tailcall il relcompat obj il relcompat obj cmd jit methodical tailcall il relcompat v il relcompat v cmd jit methodical tailcall il reldeep array il reldeep array cmd jit methodical tailcall il reldeep array nz il reldeep array nz cmd jit methodical tailcall il reldeep gc il reldeep gc cmd jit methodical tailcall il reldeep inst il reldeep inst cmd jit methodical tailcall il reldeep value il reldeep value cmd jit methodical tailcall il reldeep virt il reldeep virt cmd jit methodical tailcall il relgcval il relgcval cmd jit methodical tailcall il relgcval nested il relgcval nested cmd jit methodical tailcall il relgcval sideeffect il relgcval sideeffect cmd jit methodical tailcall il relrecurse ep il relrecurse ep cmd jit methodical tailcall il relrecurse ep void il relrecurse ep void cmd jit methodical tailcall il relreference i il relreference i cmd jit methodical tailcall il reltest il reltest cmd jit methodical tailcall il reltest il reltest cmd jit methodical tailcall il reltest il reltest cmd jit methodical tailcall il reltest implicit il reltest implicit cmd jit methodical tailcall il reltest mutual rec il reltest mutual rec cmd jit methodical tailcall il reltest switch il reltest switch cmd jit methodical tailcall il reltest virt il reltest virt cmd jit methodical tailcall il reltest void il reltest void cmd jit methodical tailcall delegatetail delegatetail cmd jit methodical tailcall tailcall av tailcall av cmd jit methodical vt callconv il il cmd jit methodical vt callconv il il cmd jit methodical vt callconv il il cmd jit methodical vt callconv il dbgvtret il dbgvtret cmd jit methodical vt callconv il il cmd jit methodical vt callconv il il cmd jit methodical vt callconv il il cmd jit methodical vt callconv il il cmd jit methodical vt callconv il relvtret il relvtret cmd jit methodical vt callconv il il cmd jit opt etw tailcallcases tailcallcases cmd jit regression clr jit pdc cmd jit regression clr jit pdc cmd jit regression clr jit cmd jit regression clr jit cmd jit regression jitblue devdiv devdiv devdiv cmd jit regression jitblue github github github cmd jit regression vs jit cmd jit regression vs jit cmd jit regression vs jit cmd jit regression vs jit cmd jit regression vs jit cmd jit regression vs jit cmd jit regression vs jit cmd | 0 |
96,004 | 27,717,782,329 | IssuesEvent | 2023-03-14 18:07:22 | alan-turing-institute/the-turing-way | https://api.github.com/repos/alan-turing-institute/the-turing-way | closed | [BUG] `[etoc] missing index.html written as redirect to 'welcome.html'` build note | bug book-build infrastructure caretaking | @aleesteele: https://github.com/alan-turing-institute/the-turing-way/pull/2883#issuecomment-1326225433 :
> Tagging @da5nsy here, getting the error `[etoc] missing index.html written as redirect to 'welcome.html'` build error? Not sure why that might be the case?
This does not cause the CI to fail, so not urgent, but...
- My best guess is that that warning occurs because of this issue: https://github.com/executablebooks/sphinx-external-toc/issues/50 in which case we would need to clear out the cache at netlify.
- My second best guess is that it is because we have `root:` and `format:` in the opposite order in [our TOC](https://github.com/alan-turing-institute/the-turing-way/blame/main/book/website/_toc.yml) vs the [JB docs](https://jupyterbook.org/en/stable/structure/configure.html?highlight=index#configure-all-entries-in-the-toc). | 1.0 | [BUG] `[etoc] missing index.html written as redirect to 'welcome.html'` build note - @aleesteele: https://github.com/alan-turing-institute/the-turing-way/pull/2883#issuecomment-1326225433 :
> Tagging @da5nsy here, getting the error `[etoc] missing index.html written as redirect to 'welcome.html'` build error? Not sure why that might be the case?
This does not cause the CI to fail, so not urgent, but...
- My best guess is that that warning occurs because of this issue: https://github.com/executablebooks/sphinx-external-toc/issues/50 in which case we would need to clear out the cache at netlify.
- My second best guess is that it is because we have `root:` and `format:` in the opposite order in [our TOC](https://github.com/alan-turing-institute/the-turing-way/blame/main/book/website/_toc.yml) vs the [JB docs](https://jupyterbook.org/en/stable/structure/configure.html?highlight=index#configure-all-entries-in-the-toc). | non_priority | missing index html written as redirect to welcome html build note aleesteele tagging here getting the error missing index html written as redirect to welcome html build error not sure why that might be the case this does not cause the ci to fail so not urgent but my best guess is that that warning occurs because of this issue in which case we would need to clear out the cache at netlify my second best guess is that it is because we have root and format in the opposite order in vs the | 0 |
17,681 | 10,112,587,578 | IssuesEvent | 2019-07-30 14:58:56 | MicrosoftDocs/windows-itpro-docs | https://api.github.com/repos/MicrosoftDocs/windows-itpro-docs | closed | Confusing | security | This section is confusing ... the If and Otherwise sections don't blend together in a paragraph. If you use AD Connect and sync (usernames only,) and have ADFS on Prem, which you redirect users to can you still use Azure MFA Cloud Service? Or do we have to use the MFA Adapter?
If your Azure AD Connect is configured to synchronize identities (usernames only), then your users are redirected to your local on-premises federation server for authentication and then redirected back to the Azure MFA cloud service. Otherwise, your Azure AD Connect is configured to synchronize credentials (username and passwords), which enables your users to authenticate to Azure Active Directory and use the Azure MFA cloud service. If you choose to use the Azure MFA cloud service directly, write Azure MFA in box 1f on your planning worksheet.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 5739fab2-c6db-a7a9-b0e7-2bf4b85912a7
* Version Independent ID: 82c58053-c1d7-d938-1b0f-f3f7f70ada3b
* Content: [Planning a Windows Hello for Business Deployment](https://docs.microsoft.com/en-us/windows/security/identity-protection/hello-for-business/hello-planning-guide#feedback)
* Content Source: [windows/security/identity-protection/hello-for-business/hello-planning-guide.md](https://github.com/MicrosoftDocs/windows-itpro-docs/blob/master/windows/security/identity-protection/hello-for-business/hello-planning-guide.md)
* Product: **w10**
* Technology: **windows**
* GitHub Login: @mapalko
* Microsoft Alias: **mapalko** | True | Confusing - This section is confusing ... the If and Otherwise sections don't blend together in a paragraph. If you use AD Connect and sync (usernames only,) and have ADFS on Prem, which you redirect users to can you still use Azure MFA Cloud Service? Or do we have to use the MFA Adapter?
If your Azure AD Connect is configured to synchronize identities (usernames only), then your users are redirected to your local on-premises federation server for authentication and then redirected back to the Azure MFA cloud service. Otherwise, your Azure AD Connect is configured to synchronize credentials (username and passwords), which enables your users to authenticate to Azure Active Directory and use the Azure MFA cloud service. If you choose to use the Azure MFA cloud service directly, write Azure MFA in box 1f on your planning worksheet.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 5739fab2-c6db-a7a9-b0e7-2bf4b85912a7
* Version Independent ID: 82c58053-c1d7-d938-1b0f-f3f7f70ada3b
* Content: [Planning a Windows Hello for Business Deployment](https://docs.microsoft.com/en-us/windows/security/identity-protection/hello-for-business/hello-planning-guide#feedback)
* Content Source: [windows/security/identity-protection/hello-for-business/hello-planning-guide.md](https://github.com/MicrosoftDocs/windows-itpro-docs/blob/master/windows/security/identity-protection/hello-for-business/hello-planning-guide.md)
* Product: **w10**
* Technology: **windows**
* GitHub Login: @mapalko
* Microsoft Alias: **mapalko** | non_priority | confusing this section is confusing the if and otherwise sections don t blend together in a paragraph if you use ad connect and sync usernames only and have adfs on prem which you redirect users to can you still use azure mfa cloud service or do we have to use the mfa adapter if your azure ad connect is configured to synchronize identities usernames only then your users are redirected to your local on premises federation server for authentication and then redirected back to the azure mfa cloud service otherwise your azure ad connect is configured to synchronize credentials username and passwords which enables your users to authenticate to azure active directory and use the azure mfa cloud service if you choose to use the azure mfa cloud service directly write azure mfa in box on your planning worksheet document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source product technology windows github login mapalko microsoft alias mapalko | 0 |
188,463 | 22,046,454,402 | IssuesEvent | 2022-05-30 02:39:57 | nlamirault/alan | https://api.github.com/repos/nlamirault/alan | opened | CVE-2022-30123 (Medium) detected in rack-1.6.9.gem | security vulnerability | ## CVE-2022-30123 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>rack-1.6.9.gem</b></p></summary>
<p>Rack provides a minimal, modular and adaptable interface for developing
web applications in Ruby. By wrapping HTTP requests and responses in
the simplest way possible, it unifies and distills the API for web
servers, web frameworks, and software in between (the so-called
middleware) into a single method call.
Also see http://rack.github.io/.
</p>
<p>Library home page: <a href="https://rubygems.org/gems/rack-1.6.9.gem">https://rubygems.org/gems/rack-1.6.9.gem</a></p>
<p>
Dependency Hierarchy:
- middleman-hashicorp-0.3.30.gem (Root Library)
- middleman-syntax-3.0.0.gem
- middleman-core-3.4.1.gem
- :x: **rack-1.6.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nlamirault/alan/commit/9060713df80212ee5546b36d1083fb607520eb0b">9060713df80212ee5546b36d1083fb607520eb0b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
There is a possible shell escape sequence injection vulnerability in the Lint and CommonLogger components of Rack before 2.0.9.1,2.1.4.1,2.2.3.1
<p>Publish Date: 2022-05-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-30123>CVE-2022-30123</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-wq4h-7r42-5hrr">https://github.com/advisories/GHSA-wq4h-7r42-5hrr</a></p>
<p>Release Date: 2022-05-03</p>
<p>Fix Resolution: rack - 2.0.9.1,2.1.4.1,2.2.3.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-30123 (Medium) detected in rack-1.6.9.gem - ## CVE-2022-30123 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>rack-1.6.9.gem</b></p></summary>
<p>Rack provides a minimal, modular and adaptable interface for developing
web applications in Ruby. By wrapping HTTP requests and responses in
the simplest way possible, it unifies and distills the API for web
servers, web frameworks, and software in between (the so-called
middleware) into a single method call.
Also see http://rack.github.io/.
</p>
<p>Library home page: <a href="https://rubygems.org/gems/rack-1.6.9.gem">https://rubygems.org/gems/rack-1.6.9.gem</a></p>
<p>
Dependency Hierarchy:
- middleman-hashicorp-0.3.30.gem (Root Library)
- middleman-syntax-3.0.0.gem
- middleman-core-3.4.1.gem
- :x: **rack-1.6.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nlamirault/alan/commit/9060713df80212ee5546b36d1083fb607520eb0b">9060713df80212ee5546b36d1083fb607520eb0b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
There is a possible shell escape sequence injection vulnerability in the Lint and CommonLogger components of Rack before 2.0.9.1,2.1.4.1,2.2.3.1
<p>Publish Date: 2022-05-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-30123>CVE-2022-30123</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-wq4h-7r42-5hrr">https://github.com/advisories/GHSA-wq4h-7r42-5hrr</a></p>
<p>Release Date: 2022-05-03</p>
<p>Fix Resolution: rack - 2.0.9.1,2.1.4.1,2.2.3.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in rack gem cve medium severity vulnerability vulnerable library rack gem rack provides a minimal modular and adaptable interface for developing web applications in ruby by wrapping http requests and responses in the simplest way possible it unifies and distills the api for web servers web frameworks and software in between the so called middleware into a single method call also see library home page a href dependency hierarchy middleman hashicorp gem root library middleman syntax gem middleman core gem x rack gem vulnerable library found in head commit a href found in base branch master vulnerability details there is a possible shell escape sequence injection vulnerability in the lint and commonlogger components of rack before publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rack step up your open source security game with mend | 0 |
5,625 | 8,481,800,181 | IssuesEvent | 2018-10-25 16:40:53 | googleapis/google-cloud-node | https://api.github.com/repos/googleapis/google-cloud-node | closed | Investigate remaining Kokoro failures | type: process | - [x] https://github.com/googleapis/nodejs-translate/pull/127 - translate requires an `API_KEY` in it's env var config.
- [x] https://github.com/googleapis/nodejs-os-login/pull/76 - all of the kokoro tests seemed to hang
- [x] https://github.com/googleapis/nodejs-dns/pull/110 - system tests are failing. I think there's an env var in circleCI we need to bring over.
- [x] https://github.com/googleapis/nodejs-dlp/pull/144 - not sure why, the samples tests are failing
- [ ] https://github.com/googleapis/nodejs-storage/pull/406 - the system tests are failing here
- [x] https://github.com/googleapis/nodejs-dialogflow/pull/171 - no backend config
- [ ] https://github.com/googleapis/nodejs-logging/pull/225 - needs an updated synth file
| 1.0 | Investigate remaining Kokoro failures - - [x] https://github.com/googleapis/nodejs-translate/pull/127 - translate requires an `API_KEY` in it's env var config.
- [x] https://github.com/googleapis/nodejs-os-login/pull/76 - all of the kokoro tests seemed to hang
- [x] https://github.com/googleapis/nodejs-dns/pull/110 - system tests are failing. I think there's an env var in circleCI we need to bring over.
- [x] https://github.com/googleapis/nodejs-dlp/pull/144 - not sure why, the samples tests are failing
- [ ] https://github.com/googleapis/nodejs-storage/pull/406 - the system tests are failing here
- [x] https://github.com/googleapis/nodejs-dialogflow/pull/171 - no backend config
- [ ] https://github.com/googleapis/nodejs-logging/pull/225 - needs an updated synth file
| non_priority | investigate remaining kokoro failures translate requires an api key in it s env var config all of the kokoro tests seemed to hang system tests are failing i think there s an env var in circleci we need to bring over not sure why the samples tests are failing the system tests are failing here no backend config needs an updated synth file | 0 |
179,280 | 14,700,258,519 | IssuesEvent | 2021-01-04 09:56:04 | kyma-project/kyma | https://api.github.com/repos/kyma-project/kyma | closed | Rework of the navigation structure in Kyma Console requires changes in the docs | area/documentation bug | <!-- Thank you for your contribution. Before you submit the issue:
1. Search open and closed issues for duplicates.
2. Read the contributing guidelines.
3. Assign the Documentation project.
-->
**Description**
As the navigation panel in the Kyma Console has been [reworked](https://github.com/kyma-project/console/pull/2074), the documentation referring to the Kyma Console and mentioning the navigation panel must be updated as well. There are still some references to the old structure both in the Getting Started Guides and in the Kyma docs. As part of this issue, locate all the references to the old structure and correct them.
**Area**
area/documentation
**Reasons**
Documentation must be up-to-date and reflect the current navigation structure on the Kyma Console.
**Assignees**
@kyma-project/technical-writers
**Attachments**
The new navigation panel:

One of the outdated docs:

| 1.0 | Rework of the navigation structure in Kyma Console requires changes in the docs - <!-- Thank you for your contribution. Before you submit the issue:
1. Search open and closed issues for duplicates.
2. Read the contributing guidelines.
3. Assign the Documentation project.
-->
**Description**
As the navigation panel in the Kyma Console has been [reworked](https://github.com/kyma-project/console/pull/2074), the documentation referring to the Kyma Console and mentioning the navigation panel must be updated as well. There are still some references to the old structure both in the Getting Started Guides and in the Kyma docs. As part of this issue, locate all the references to the old structure and correct them.
**Area**
area/documentation
**Reasons**
Documentation must be up-to-date and reflect the current navigation structure on the Kyma Console.
**Assignees**
@kyma-project/technical-writers
**Attachments**
The new navigation panel:

One of the outdated docs:

| non_priority | rework of the navigation structure in kyma console requires changes in the docs thank you for your contribution before you submit the issue search open and closed issues for duplicates read the contributing guidelines assign the documentation project description as the navigation panel in the kyma console has been the documentation referring to the kyma console and mentioning the navigation panel must be updated as well there are still some references to the old structure both in the getting started guides and in the kyma docs as part of this issue locate all the references to the old structure and correct them area area documentation reasons documentation must be up to date and reflect the current navigation structure on the kyma console assignees kyma project technical writers attachments the new navigation panel one of the outdated docs | 0 |
18,038 | 10,188,668,119 | IssuesEvent | 2019-08-11 13:05:02 | rengert/bolzplatzarena.startup | https://api.github.com/repos/rengert/bolzplatzarena.startup | closed | WS-2019-0063 (High) detected in js-yaml-3.12.1.tgz | security vulnerability | ## WS-2019-0063 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>js-yaml-3.12.1.tgz</b></p></summary>
<p>YAML 1.2 parser and serializer</p>
<p>Library home page: <a href="https://registry.npmjs.org/js-yaml/-/js-yaml-3.12.1.tgz">https://registry.npmjs.org/js-yaml/-/js-yaml-3.12.1.tgz</a></p>
<p>Path to dependency file: /bolzplatzarena.startup/src/Bolzplatzarena.Startup.App/package.json</p>
<p>Path to vulnerable library: /tmp/git/bolzplatzarena.startup/src/Bolzplatzarena.Startup.App/node_modules/js-yaml/package.json</p>
<p>
Dependency Hierarchy:
- karma-coverage-istanbul-reporter-2.0.5.tgz (Root Library)
- istanbul-api-2.1.1.tgz
- :x: **js-yaml-3.12.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rengert/bolzplatzarena.startup/commit/2c62c904e248d8a03984e11655083af394ed3fec">2c62c904e248d8a03984e11655083af394ed3fec</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Js-yaml prior to 3.13.1 are vulnerable to Code Injection. The load() function may execute arbitrary code injected through a malicious YAML file.
<p>Publish Date: 2019-04-30
<p>URL: <a href=https://github.com/nodeca/js-yaml/pull/480>WS-2019-0063</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>8.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/813">https://www.npmjs.com/advisories/813</a></p>
<p>Release Date: 2019-04-30</p>
<p>Fix Resolution: 3.13.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0063 (High) detected in js-yaml-3.12.1.tgz - ## WS-2019-0063 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>js-yaml-3.12.1.tgz</b></p></summary>
<p>YAML 1.2 parser and serializer</p>
<p>Library home page: <a href="https://registry.npmjs.org/js-yaml/-/js-yaml-3.12.1.tgz">https://registry.npmjs.org/js-yaml/-/js-yaml-3.12.1.tgz</a></p>
<p>Path to dependency file: /bolzplatzarena.startup/src/Bolzplatzarena.Startup.App/package.json</p>
<p>Path to vulnerable library: /tmp/git/bolzplatzarena.startup/src/Bolzplatzarena.Startup.App/node_modules/js-yaml/package.json</p>
<p>
Dependency Hierarchy:
- karma-coverage-istanbul-reporter-2.0.5.tgz (Root Library)
- istanbul-api-2.1.1.tgz
- :x: **js-yaml-3.12.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rengert/bolzplatzarena.startup/commit/2c62c904e248d8a03984e11655083af394ed3fec">2c62c904e248d8a03984e11655083af394ed3fec</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Js-yaml prior to 3.13.1 are vulnerable to Code Injection. The load() function may execute arbitrary code injected through a malicious YAML file.
<p>Publish Date: 2019-04-30
<p>URL: <a href=https://github.com/nodeca/js-yaml/pull/480>WS-2019-0063</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>8.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/813">https://www.npmjs.com/advisories/813</a></p>
<p>Release Date: 2019-04-30</p>
<p>Fix Resolution: 3.13.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws high detected in js yaml tgz ws high severity vulnerability vulnerable library js yaml tgz yaml parser and serializer library home page a href path to dependency file bolzplatzarena startup src bolzplatzarena startup app package json path to vulnerable library tmp git bolzplatzarena startup src bolzplatzarena startup app node modules js yaml package json dependency hierarchy karma coverage istanbul reporter tgz root library istanbul api tgz x js yaml tgz vulnerable library found in head commit a href vulnerability details js yaml prior to are vulnerable to code injection the load function may execute arbitrary code injected through a malicious yaml file publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
36,205 | 5,039,017,830 | IssuesEvent | 2016-12-18 15:48:09 | USQ-Media-Services/animated-screening-project | https://api.github.com/repos/USQ-Media-Services/animated-screening-project | closed | Test: Selected check box - Favourites page | features test | When selected the checkbox should display a green tick box item if enabled. | 1.0 | Test: Selected check box - Favourites page - When selected the checkbox should display a green tick box item if enabled. | non_priority | test selected check box favourites page when selected the checkbox should display a green tick box item if enabled | 0 |
125,107 | 16,724,640,169 | IssuesEvent | 2021-06-10 11:31:49 | JGL/WalkingTourClient | https://api.github.com/repos/JGL/WalkingTourClient | closed | Let's try ar.js out again - they seemed to have added location based code? | design | https://github.com/AR-js-org/AR.js#location-based-example
Location based? | 1.0 | Let's try ar.js out again - they seemed to have added location based code? - https://github.com/AR-js-org/AR.js#location-based-example
Location based? | non_priority | let s try ar js out again they seemed to have added location based code location based | 0 |
50,273 | 13,187,416,225 | IssuesEvent | 2020-08-13 03:20:42 | icecube-trac/tix3 | https://api.github.com/repos/icecube-trac/tix3 | closed | Minor typo in I3Time.cxx (Trac #434) | Migrated from Trac dataclasses defect | This line: http://code.icecube.wisc.edu/projects/icecube/browser/projects/dataclasses/trunk/private/dataclasses/I3Time.cxx#L120
Should read
```text
if (ns <0 || ns >= I3Units::second )
```
instead of
```text
if (ns <0 || sec >= I3Units::second )
```
<details>
<summary>_Migrated from https://code.icecube.wisc.edu/ticket/434
, reported by kislat and owned by blaufuss_</summary>
<p>
```json
{
"status": "closed",
"changetime": "2012-07-27T21:34:03",
"description": "This line: http://code.icecube.wisc.edu/projects/icecube/browser/projects/dataclasses/trunk/private/dataclasses/I3Time.cxx#L120\n\nShould read\n\n{{{\nif (ns <0 || ns >= I3Units::second )\n}}}\n\ninstead of\n\n{{{\nif (ns <0 || sec >= I3Units::second )\n}}}",
"reporter": "kislat",
"cc": "",
"resolution": "fixed",
"_ts": "1343424843000000",
"component": "dataclasses",
"summary": "Minor typo in I3Time.cxx",
"priority": "trivial",
"keywords": "",
"time": "2012-07-19T22:56:16",
"milestone": "",
"owner": "blaufuss",
"type": "defect"
}
```
</p>
</details>
| 1.0 | Minor typo in I3Time.cxx (Trac #434) - This line: http://code.icecube.wisc.edu/projects/icecube/browser/projects/dataclasses/trunk/private/dataclasses/I3Time.cxx#L120
Should read
```text
if (ns <0 || ns >= I3Units::second )
```
instead of
```text
if (ns <0 || sec >= I3Units::second )
```
<details>
<summary>_Migrated from https://code.icecube.wisc.edu/ticket/434
, reported by kislat and owned by blaufuss_</summary>
<p>
```json
{
"status": "closed",
"changetime": "2012-07-27T21:34:03",
"description": "This line: http://code.icecube.wisc.edu/projects/icecube/browser/projects/dataclasses/trunk/private/dataclasses/I3Time.cxx#L120\n\nShould read\n\n{{{\nif (ns <0 || ns >= I3Units::second )\n}}}\n\ninstead of\n\n{{{\nif (ns <0 || sec >= I3Units::second )\n}}}",
"reporter": "kislat",
"cc": "",
"resolution": "fixed",
"_ts": "1343424843000000",
"component": "dataclasses",
"summary": "Minor typo in I3Time.cxx",
"priority": "trivial",
"keywords": "",
"time": "2012-07-19T22:56:16",
"milestone": "",
"owner": "blaufuss",
"type": "defect"
}
```
</p>
</details>
| non_priority | minor typo in cxx trac this line should read text if ns second instead of text if ns second migrated from reported by kislat and owned by blaufuss json status closed changetime description this line read n n nif ns second n n ninstead of n n nif ns second n reporter kislat cc resolution fixed ts component dataclasses summary minor typo in cxx priority trivial keywords time milestone owner blaufuss type defect | 0 |
256,986 | 19,484,086,561 | IssuesEvent | 2021-12-26 01:34:57 | TheCaptain989/radarr-striptracks | https://api.github.com/repos/TheCaptain989/radarr-striptracks | opened | Radarr and Sonarr treat languages so differently | documentation | In my quest to make my script more and more automatic so that it does things on its own that I find myself doing by hand, I decided to tackle languages a while back. I started by using the built-in functions in Radarr and Sonarr v3 that allow for languages in configured profiles.
I soon found that each program treats languages very differently:
- Radarr ties the download language to the _Quality Profile_, and you can only choose one language.
- Sonarr has a download separate _Language Profile_, and you can select multiple languages.
I also found that in addition to natural language selections, each also has an 'Unknown' selection. That sounded nice.
Radarr also has 'Any' and 'Original' selections that Sonarr doesn't have, which as far as I can tell do the exact same thing. There is nowhere in the GUI or the returned JSON in Radarr where it tracks the first release language of a movie, so 'Original' can't do what you would think it does.
So, I worked out how to call the APIs and parse the JSON, added some more variables to differentiate between them, and how to work with effectively two 'Any' settings in Radarr.
### Release 2.0 was born.
---
This worked out really great. However, after a bit, I found myself manually updating the Languages on movies in Radarr when "Multi-Language" appeared. Unless they were foreign films, this turned out to be an indicator that the movie had been detected with more than one audio language during download, but after remuxing, only retained one language (or a smaller set of languages).
How hard could that be?
☹️ 🤦♂️
I have now thoroughly unpacked the problem, only to discover that yet again, Radarr and Sonarr treat languages very differently:
- Sonarr allows only _one language_ on each episode file
- Radarr allows a selection of multiple languages per movie file
Exactly the opposite of the profile issue above.
`<rant on>`
They have _opposite_ issues??? One allows the selection of multiple languages during download, but only one language configured per file, while the other allows the selection of only one language during download, but multiple languages configured per file!
**WTF?!?**
How hard can it be to get both Radarr and Sonarr to treat languages the same !@#$% way! Sheesh.
This is just the **dumbest** thing.
`<end rant>`
After much tweaking, dealing with JSON differences, etc.,
### Please help test Release 2.2 that attempts to deal with this cluster f--- | 1.0 | Radarr and Sonarr treat languages so differently - In my quest to make my script more and more automatic so that it does things on its own that I find myself doing by hand, I decided to tackle languages a while back. I started by using the built-in functions in Radarr and Sonarr v3 that allow for languages in configured profiles.
I soon found that each program treats languages very differently:
- Radarr ties the download language to the _Quality Profile_, and you can only choose one language.
- Sonarr has a download separate _Language Profile_, and you can select multiple languages.
I also found that in addition to natural language selections, each also has an 'Unknown' selection. That sounded nice.
Radarr also has 'Any' and 'Original' selections that Sonarr doesn't have, which as far as I can tell do the exact same thing. There is nowhere in the GUI or the returned JSON in Radarr where it tracks the first release language of a movie, so 'Original' can't do what you would think it does.
So, I worked out how to call the APIs and parse the JSON, added some more variables to differentiate between them, and how to work with effectively two 'Any' settings in Radarr.
### Release 2.0 was born.
---
This worked out really great. However, after a bit, I found myself manually updating the Languages on movies in Radarr when "Multi-Language" appeared. Unless they were foreign films, this turned out to be an indicator that the movie had been detected with more than one audio language during download, but after remuxing, only retained one language (or a smaller set of languages).
How hard could that be?
☹️ 🤦♂️
I have now thoroughly unpacked the problem, only to discover that yet again, Radarr and Sonarr treat languages very differently:
- Sonarr allows only _one language_ on each episode file
- Radarr allows a selection of multiple languages per movie file
Exactly the opposite of the profile issue above.
`<rant on>`
They have _opposite_ issues??? One allows the selection of multiple languages during download, but only one language configured per file, while the other allows the selection of only one language during download, but multiple languages configured per file!
**WTF?!?**
How hard can it be to get both Radarr and Sonarr to treat languages the same !@#$% way! Sheesh.
This is just the **dumbest** thing.
`<end rant>`
After much tweaking, dealing with JSON differences, etc.,
### Please help test Release 2.2 that attempts to deal with this cluster f--- | non_priority | radarr and sonarr treat languages so differently in my quest to make my script more and more automatic so that it does things on its own that i find myself doing by hand i decided to tackle languages a while back i started by using the built in functions in radarr and sonarr that allow for languages in configured profiles i soon found that each program treats languages very differently radarr ties the download language to the quality profile and you can only choose one language sonarr has a download separate language profile and you can select multiple languages i also found that in addition to natural language selections each also has an unknown selection that sounded nice radarr also has any and original selections that sonarr doesn t have which as far as i can tell do the exact same thing there is nowhere in the gui or the returned json in radarr where it tracks the first release language of a movie so original can t do what you would think it does so i worked out how to call the apis and parse the json added some more variables to differentiate between them and how to work with effectively two any settings in radarr release was born this worked out really great however after a bit i found myself manually updating the languages on movies in radarr when multi language appeared unless they were foreign films this turned out to be an indicator that the movie had been detected with more than one audio language during download but after remuxing only retained one language or a smaller set of languages how hard could that be ☹️ 🤦♂️ i have now thoroughly unpacked the problem only to discover that yet again radarr and sonarr treat languages very differently sonarr allows only one language on each episode file radarr allows a selection of multiple languages per movie file exactly the opposite of the profile issue above they have opposite issues one allows the selection of multiple languages during download but only one language configured per file while the other allows the selection of only one language during download but multiple languages configured per file wtf how hard can it be to get both radarr and sonarr to treat languages the same way sheesh this is just the dumbest thing after much tweaking dealing with json differences etc please help test release that attempts to deal with this cluster f | 0 |
141,057 | 12,955,832,738 | IssuesEvent | 2020-07-20 07:09:08 | lambda-my-aws/ecs_composex | https://api.github.com/repos/lambda-my-aws/ecs_composex | closed | Error in ecs_composex/ecs/SYNTAX.rst#L90 | documentation enhancement | **Is your feature request related to a problem? Please describe.**
Since the change to `lb_type`, `use_alb` and `use_nlb` is no longer necessary.
**Describe the solution you'd like**
Correct the documentation
| 1.0 | Error in ecs_composex/ecs/SYNTAX.rst#L90 - **Is your feature request related to a problem? Please describe.**
Since the change to `lb_type`, `use_alb` and `use_nlb` is no longer necessary.
**Describe the solution you'd like**
Correct the documentation
| non_priority | error in ecs composex ecs syntax rst is your feature request related to a problem please describe since the change to lb type use alb and use nlb is no longer necessary describe the solution you d like correct the documentation | 0 |
103,477 | 16,602,892,514 | IssuesEvent | 2021-06-01 22:13:22 | gms-ws-sandbox/nibrs | https://api.github.com/repos/gms-ws-sandbox/nibrs | opened | CVE-2020-15250 (Medium) detected in junit-4.10.jar, junit-4.12.jar | security vulnerability | ## CVE-2020-15250 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>junit-4.10.jar</b>, <b>junit-4.12.jar</b></p></summary>
<p>
<details><summary><b>junit-4.10.jar</b></p></summary>
<p>JUnit is a regression testing framework written by Erich Gamma and Kent Beck.
It is used by the developer who implements unit tests in Java.</p>
<p>Library home page: <a href="http://junit.org">http://junit.org</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-validate-common/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/junit/junit/4.10/junit-4.10.jar,canner/.m2/repository/junit/junit/4.10/junit-4.10.jar,canner/.m2/repository/junit/junit/4.10/junit-4.10.jar</p>
<p>
Dependency Hierarchy:
- :x: **junit-4.10.jar** (Vulnerable Library)
</details>
<details><summary><b>junit-4.12.jar</b></p></summary>
<p>JUnit is a unit testing framework for Java, created by Erich Gamma and Kent Beck.</p>
<p>Library home page: <a href="http://junit.org">http://junit.org</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-staging-data/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/junit/junit/4.12/junit-4.12.jar,/home/wss-scanner/.m2/repository/junit/junit/4.12/junit-4.12.jar,/home/wss-scanner/.m2/repository/junit/junit/4.12/junit-4.12.jar,canner/.m2/repository/junit/junit/4.12/junit-4.12.jar,/home/wss-scanner/.m2/repository/junit/junit/4.12/junit-4.12.jar,/home/wss-scanner/.m2/repository/junit/junit/4.12/junit-4.12.jar,canner/.m2/repository/junit/junit/4.12/junit-4.12.jar,nibrs/web/nibrs-web/target/nibrs-web/WEB-INF/lib/junit-4.12.jar</p>
<p>
Dependency Hierarchy:
- :x: **junit-4.12.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/gms-ws-sandbox/nibrs/commit/9fb1c19bd26c2113d1961640de126a33eacdc946">9fb1c19bd26c2113d1961640de126a33eacdc946</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In JUnit4 from version 4.7 and before 4.13.1, the test rule TemporaryFolder contains a local information disclosure vulnerability. On Unix like systems, the system's temporary directory is shared between all users on that system. Because of this, when files and directories are written into this directory they are, by default, readable by other users on that same system. This vulnerability does not allow other users to overwrite the contents of these directories or files. This is purely an information disclosure vulnerability. This vulnerability impacts you if the JUnit tests write sensitive information, like API keys or passwords, into the temporary folder, and the JUnit tests execute in an environment where the OS has other untrusted users. Because certain JDK file system APIs were only added in JDK 1.7, this this fix is dependent upon the version of the JDK you are using. For Java 1.7 and higher users: this vulnerability is fixed in 4.13.1. For Java 1.6 and lower users: no patch is available, you must use the workaround below. If you are unable to patch, or are stuck running on Java 1.6, specifying the `java.io.tmpdir` system environment variable to a directory that is exclusively owned by the executing user will fix this vulnerability. For more information, including an example of vulnerable code, see the referenced GitHub Security Advisory.
<p>Publish Date: 2020-10-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15250>CVE-2020-15250</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/junit-team/junit4/security/advisories/GHSA-269g-pwp5-87pp">https://github.com/junit-team/junit4/security/advisories/GHSA-269g-pwp5-87pp</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: junit:junit:4.13.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"junit","packageName":"junit","packageVersion":"4.10","packageFilePaths":["/tools/nibrs-validate-common/pom.xml","/tools/nibrs-flatfile/pom.xml","/tools/nibrs-common/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"junit:junit:4.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"junit:junit:4.13.1"},{"packageType":"Java","groupId":"junit","packageName":"junit","packageVersion":"4.12","packageFilePaths":["/tools/nibrs-staging-data/pom.xml","/tools/nibrs-summary-report/pom.xml","/tools/nibrs-validation/pom.xml","/tools/nibrs-staging-data-common/pom.xml","/tools/nibrs-fbi-service/pom.xml","/tools/nibrs-summary-report-common/pom.xml","/tools/nibrs-xmlfile/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"junit:junit:4.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"junit:junit:4.13.1"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-15250","vulnerabilityDetails":"In JUnit4 from version 4.7 and before 4.13.1, the test rule TemporaryFolder contains a local information disclosure vulnerability. On Unix like systems, the system\u0027s temporary directory is shared between all users on that system. Because of this, when files and directories are written into this directory they are, by default, readable by other users on that same system. This vulnerability does not allow other users to overwrite the contents of these directories or files. This is purely an information disclosure vulnerability. This vulnerability impacts you if the JUnit tests write sensitive information, like API keys or passwords, into the temporary folder, and the JUnit tests execute in an environment where the OS has other untrusted users. Because certain JDK file system APIs were only added in JDK 1.7, this this fix is dependent upon the version of the JDK you are using. For Java 1.7 and higher users: this vulnerability is fixed in 4.13.1. For Java 1.6 and lower users: no patch is available, you must use the workaround below. If you are unable to patch, or are stuck running on Java 1.6, specifying the `java.io.tmpdir` system environment variable to a directory that is exclusively owned by the executing user will fix this vulnerability. For more information, including an example of vulnerable code, see the referenced GitHub Security Advisory.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15250","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-15250 (Medium) detected in junit-4.10.jar, junit-4.12.jar - ## CVE-2020-15250 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>junit-4.10.jar</b>, <b>junit-4.12.jar</b></p></summary>
<p>
<details><summary><b>junit-4.10.jar</b></p></summary>
<p>JUnit is a regression testing framework written by Erich Gamma and Kent Beck.
It is used by the developer who implements unit tests in Java.</p>
<p>Library home page: <a href="http://junit.org">http://junit.org</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-validate-common/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/junit/junit/4.10/junit-4.10.jar,canner/.m2/repository/junit/junit/4.10/junit-4.10.jar,canner/.m2/repository/junit/junit/4.10/junit-4.10.jar</p>
<p>
Dependency Hierarchy:
- :x: **junit-4.10.jar** (Vulnerable Library)
</details>
<details><summary><b>junit-4.12.jar</b></p></summary>
<p>JUnit is a unit testing framework for Java, created by Erich Gamma and Kent Beck.</p>
<p>Library home page: <a href="http://junit.org">http://junit.org</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-staging-data/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/junit/junit/4.12/junit-4.12.jar,/home/wss-scanner/.m2/repository/junit/junit/4.12/junit-4.12.jar,/home/wss-scanner/.m2/repository/junit/junit/4.12/junit-4.12.jar,canner/.m2/repository/junit/junit/4.12/junit-4.12.jar,/home/wss-scanner/.m2/repository/junit/junit/4.12/junit-4.12.jar,/home/wss-scanner/.m2/repository/junit/junit/4.12/junit-4.12.jar,canner/.m2/repository/junit/junit/4.12/junit-4.12.jar,nibrs/web/nibrs-web/target/nibrs-web/WEB-INF/lib/junit-4.12.jar</p>
<p>
Dependency Hierarchy:
- :x: **junit-4.12.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/gms-ws-sandbox/nibrs/commit/9fb1c19bd26c2113d1961640de126a33eacdc946">9fb1c19bd26c2113d1961640de126a33eacdc946</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In JUnit4 from version 4.7 and before 4.13.1, the test rule TemporaryFolder contains a local information disclosure vulnerability. On Unix like systems, the system's temporary directory is shared between all users on that system. Because of this, when files and directories are written into this directory they are, by default, readable by other users on that same system. This vulnerability does not allow other users to overwrite the contents of these directories or files. This is purely an information disclosure vulnerability. This vulnerability impacts you if the JUnit tests write sensitive information, like API keys or passwords, into the temporary folder, and the JUnit tests execute in an environment where the OS has other untrusted users. Because certain JDK file system APIs were only added in JDK 1.7, this this fix is dependent upon the version of the JDK you are using. For Java 1.7 and higher users: this vulnerability is fixed in 4.13.1. For Java 1.6 and lower users: no patch is available, you must use the workaround below. If you are unable to patch, or are stuck running on Java 1.6, specifying the `java.io.tmpdir` system environment variable to a directory that is exclusively owned by the executing user will fix this vulnerability. For more information, including an example of vulnerable code, see the referenced GitHub Security Advisory.
<p>Publish Date: 2020-10-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15250>CVE-2020-15250</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/junit-team/junit4/security/advisories/GHSA-269g-pwp5-87pp">https://github.com/junit-team/junit4/security/advisories/GHSA-269g-pwp5-87pp</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: junit:junit:4.13.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"junit","packageName":"junit","packageVersion":"4.10","packageFilePaths":["/tools/nibrs-validate-common/pom.xml","/tools/nibrs-flatfile/pom.xml","/tools/nibrs-common/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"junit:junit:4.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"junit:junit:4.13.1"},{"packageType":"Java","groupId":"junit","packageName":"junit","packageVersion":"4.12","packageFilePaths":["/tools/nibrs-staging-data/pom.xml","/tools/nibrs-summary-report/pom.xml","/tools/nibrs-validation/pom.xml","/tools/nibrs-staging-data-common/pom.xml","/tools/nibrs-fbi-service/pom.xml","/tools/nibrs-summary-report-common/pom.xml","/tools/nibrs-xmlfile/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"junit:junit:4.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"junit:junit:4.13.1"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-15250","vulnerabilityDetails":"In JUnit4 from version 4.7 and before 4.13.1, the test rule TemporaryFolder contains a local information disclosure vulnerability. On Unix like systems, the system\u0027s temporary directory is shared between all users on that system. Because of this, when files and directories are written into this directory they are, by default, readable by other users on that same system. This vulnerability does not allow other users to overwrite the contents of these directories or files. This is purely an information disclosure vulnerability. This vulnerability impacts you if the JUnit tests write sensitive information, like API keys or passwords, into the temporary folder, and the JUnit tests execute in an environment where the OS has other untrusted users. Because certain JDK file system APIs were only added in JDK 1.7, this this fix is dependent upon the version of the JDK you are using. For Java 1.7 and higher users: this vulnerability is fixed in 4.13.1. For Java 1.6 and lower users: no patch is available, you must use the workaround below. If you are unable to patch, or are stuck running on Java 1.6, specifying the `java.io.tmpdir` system environment variable to a directory that is exclusively owned by the executing user will fix this vulnerability. For more information, including an example of vulnerable code, see the referenced GitHub Security Advisory.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15250","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in junit jar junit jar cve medium severity vulnerability vulnerable libraries junit jar junit jar junit jar junit is a regression testing framework written by erich gamma and kent beck it is used by the developer who implements unit tests in java library home page a href path to dependency file nibrs tools nibrs validate common pom xml path to vulnerable library home wss scanner repository junit junit junit jar canner repository junit junit junit jar canner repository junit junit junit jar dependency hierarchy x junit jar vulnerable library junit jar junit is a unit testing framework for java created by erich gamma and kent beck library home page a href path to dependency file nibrs tools nibrs staging data pom xml path to vulnerable library home wss scanner repository junit junit junit jar home wss scanner repository junit junit junit jar home wss scanner repository junit junit junit jar canner repository junit junit junit jar home wss scanner repository junit junit junit jar home wss scanner repository junit junit junit jar canner repository junit junit junit jar nibrs web nibrs web target nibrs web web inf lib junit jar dependency hierarchy x junit jar vulnerable library found in head commit a href found in base branch master vulnerability details in from version and before the test rule temporaryfolder contains a local information disclosure vulnerability on unix like systems the system s temporary directory is shared between all users on that system because of this when files and directories are written into this directory they are by default readable by other users on that same system this vulnerability does not allow other users to overwrite the contents of these directories or files this is purely an information disclosure vulnerability this vulnerability impacts you if the junit tests write sensitive information like api keys or passwords into the temporary folder and the junit tests execute in an environment where the os has other untrusted users because certain jdk file system apis were only added in jdk this this fix is dependent upon the version of the jdk you are using for java and higher users this vulnerability is fixed in for java and lower users no patch is available you must use the workaround below if you are unable to patch or are stuck running on java specifying the java io tmpdir system environment variable to a directory that is exclusively owned by the executing user will fix this vulnerability for more information including an example of vulnerable code see the referenced github security advisory publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution junit junit isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree junit junit isminimumfixversionavailable true minimumfixversion junit junit packagetype java groupid junit packagename junit packageversion packagefilepaths istransitivedependency false dependencytree junit junit isminimumfixversionavailable true minimumfixversion junit junit basebranches vulnerabilityidentifier cve vulnerabilitydetails in from version and before the test rule temporaryfolder contains a local information disclosure vulnerability on unix like systems the system temporary directory is shared between all users on that system because of this when files and directories are written into this directory they are by default readable by other users on that same system this vulnerability does not allow other users to overwrite the contents of these directories or files this is purely an information disclosure vulnerability this vulnerability impacts you if the junit tests write sensitive information like api keys or passwords into the temporary folder and the junit tests execute in an environment where the os has other untrusted users because certain jdk file system apis were only added in jdk this this fix is dependent upon the version of the jdk you are using for java and higher users this vulnerability is fixed in for java and lower users no patch is available you must use the workaround below if you are unable to patch or are stuck running on java specifying the java io tmpdir system environment variable to a directory that is exclusively owned by the executing user will fix this vulnerability for more information including an example of vulnerable code see the referenced github security advisory vulnerabilityurl | 0 |
202,464 | 23,077,297,834 | IssuesEvent | 2022-07-26 01:45:35 | turkdevops/sanity | https://api.github.com/repos/turkdevops/sanity | opened | CVE-2021-35065 (High) detected in multiple libraries | security vulnerability | ## CVE-2021-35065 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>glob-parent-5.1.2.tgz</b>, <b>glob-parent-3.1.0.tgz</b>, <b>glob-parent-2.0.0.tgz</b></p></summary>
<p>
<details><summary><b>glob-parent-5.1.2.tgz</b></p></summary>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.2.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.2.tgz</a></p>
<p>Path to dependency file: /packages/@sanity/core/package.json</p>
<p>Path to vulnerable library: /packages/@sanity/core/node_modules/watchpack/node_modules/glob-parent/package.json,/node_modules/fast-glob/node_modules/glob-parent/package.json,/packages/@sanity/mutator/node_modules/glob-parent/package.json,/packages/@sanity/form-builder/node_modules/glob-parent/package.json,/node_modules/@lerna/project/node_modules/glob-parent/package.json,/packages/@sanity/storybook/node_modules/glob-parent/package.json,/node_modules/@babel/cli/node_modules/glob-parent/package.json,/packages/@sanity/webpack-integration/node_modules/glob-parent/package.json,/packages/@sanity/util/node_modules/glob-parent/package.json,/packages/@sanity/cli/node_modules/webpack/node_modules/glob-parent/package.json,/node_modules/eslint/node_modules/glob-parent/package.json,/packages/@sanity/server/node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- add-3.21.0.tgz
- command-3.21.0.tgz
- project-3.21.0.tgz
- :x: **glob-parent-5.1.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>glob-parent-3.1.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/glob-parent/package.json,/packages/@sanity/webpack-integration/node_modules/watchpack-chokidar2/node_modules/glob-parent/package.json,/packages/@sanity/server/node_modules/watchpack-chokidar2/node_modules/glob-parent/package.json,/packages/@sanity/core/node_modules/glob-parent/package.json,/packages/@sanity/cli/node_modules/webpack/node_modules/watchpack-chokidar2/node_modules/glob-parent/package.json,/packages/@sanity/import-cli/node_modules/glob-parent/package.json,/packages/@sanity/storybook/node_modules/watchpack-chokidar2/node_modules/glob-parent/package.json,/packages/@sanity/import/node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- gulp-watch-5.0.1.tgz (Root Library)
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>glob-parent-2.0.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-2.0.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-2.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/glob-base/node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- gulp-watch-5.0.1.tgz (Root Library)
- anymatch-1.3.2.tgz
- micromatch-2.3.11.tgz
- parse-glob-3.0.4.tgz
- glob-base-0.3.0.tgz
- :x: **glob-parent-2.0.0.tgz** (Vulnerable Library)
</details>
<p>Found in base branch: <b>next</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package glob-parent before 6.0.1 are vulnerable to Regular Expression Denial of Service (ReDoS)
<p>Publish Date: 2021-06-22
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-35065>CVE-2021-35065</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-cj88-88mr-972w">https://github.com/advisories/GHSA-cj88-88mr-972w</a></p>
<p>Release Date: 2021-06-22</p>
<p>Fix Resolution (glob-parent): 6.0.1</p>
<p>Direct dependency fix Resolution (lerna): 5.1.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-35065 (High) detected in multiple libraries - ## CVE-2021-35065 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>glob-parent-5.1.2.tgz</b>, <b>glob-parent-3.1.0.tgz</b>, <b>glob-parent-2.0.0.tgz</b></p></summary>
<p>
<details><summary><b>glob-parent-5.1.2.tgz</b></p></summary>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.2.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.2.tgz</a></p>
<p>Path to dependency file: /packages/@sanity/core/package.json</p>
<p>Path to vulnerable library: /packages/@sanity/core/node_modules/watchpack/node_modules/glob-parent/package.json,/node_modules/fast-glob/node_modules/glob-parent/package.json,/packages/@sanity/mutator/node_modules/glob-parent/package.json,/packages/@sanity/form-builder/node_modules/glob-parent/package.json,/node_modules/@lerna/project/node_modules/glob-parent/package.json,/packages/@sanity/storybook/node_modules/glob-parent/package.json,/node_modules/@babel/cli/node_modules/glob-parent/package.json,/packages/@sanity/webpack-integration/node_modules/glob-parent/package.json,/packages/@sanity/util/node_modules/glob-parent/package.json,/packages/@sanity/cli/node_modules/webpack/node_modules/glob-parent/package.json,/node_modules/eslint/node_modules/glob-parent/package.json,/packages/@sanity/server/node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- add-3.21.0.tgz
- command-3.21.0.tgz
- project-3.21.0.tgz
- :x: **glob-parent-5.1.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>glob-parent-3.1.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/glob-parent/package.json,/packages/@sanity/webpack-integration/node_modules/watchpack-chokidar2/node_modules/glob-parent/package.json,/packages/@sanity/server/node_modules/watchpack-chokidar2/node_modules/glob-parent/package.json,/packages/@sanity/core/node_modules/glob-parent/package.json,/packages/@sanity/cli/node_modules/webpack/node_modules/watchpack-chokidar2/node_modules/glob-parent/package.json,/packages/@sanity/import-cli/node_modules/glob-parent/package.json,/packages/@sanity/storybook/node_modules/watchpack-chokidar2/node_modules/glob-parent/package.json,/packages/@sanity/import/node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- gulp-watch-5.0.1.tgz (Root Library)
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>glob-parent-2.0.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-2.0.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-2.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/glob-base/node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- gulp-watch-5.0.1.tgz (Root Library)
- anymatch-1.3.2.tgz
- micromatch-2.3.11.tgz
- parse-glob-3.0.4.tgz
- glob-base-0.3.0.tgz
- :x: **glob-parent-2.0.0.tgz** (Vulnerable Library)
</details>
<p>Found in base branch: <b>next</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package glob-parent before 6.0.1 are vulnerable to Regular Expression Denial of Service (ReDoS)
<p>Publish Date: 2021-06-22
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-35065>CVE-2021-35065</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-cj88-88mr-972w">https://github.com/advisories/GHSA-cj88-88mr-972w</a></p>
<p>Release Date: 2021-06-22</p>
<p>Fix Resolution (glob-parent): 6.0.1</p>
<p>Direct dependency fix Resolution (lerna): 5.1.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries glob parent tgz glob parent tgz glob parent tgz glob parent tgz extract the non magic parent path from a glob string library home page a href path to dependency file packages sanity core package json path to vulnerable library packages sanity core node modules watchpack node modules glob parent package json node modules fast glob node modules glob parent package json packages sanity mutator node modules glob parent package json packages sanity form builder node modules glob parent package json node modules lerna project node modules glob parent package json packages sanity storybook node modules glob parent package json node modules babel cli node modules glob parent package json packages sanity webpack integration node modules glob parent package json packages sanity util node modules glob parent package json packages sanity cli node modules webpack node modules glob parent package json node modules eslint node modules glob parent package json packages sanity server node modules glob parent package json dependency hierarchy lerna tgz root library add tgz command tgz project tgz x glob parent tgz vulnerable library glob parent tgz strips glob magic from a string to provide the parent directory path library home page a href path to dependency file package json path to vulnerable library node modules glob parent package json packages sanity webpack integration node modules watchpack node modules glob parent package json packages sanity server node modules watchpack node modules glob parent package json packages sanity core node modules glob parent package json packages sanity cli node modules webpack node modules watchpack node modules glob parent package json packages sanity import cli node modules glob parent package json packages sanity storybook node modules watchpack node modules glob parent package json packages sanity import node modules glob parent package json dependency hierarchy gulp watch tgz root library x glob parent tgz vulnerable library glob parent tgz strips glob magic from a string to provide the parent path library home page a href path to dependency file package json path to vulnerable library node modules glob base node modules glob parent package json dependency hierarchy gulp watch tgz root library anymatch tgz micromatch tgz parse glob tgz glob base tgz x glob parent tgz vulnerable library found in base branch next vulnerability details the package glob parent before are vulnerable to regular expression denial of service redos publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution glob parent direct dependency fix resolution lerna step up your open source security game with mend | 0 |
181,726 | 30,729,365,262 | IssuesEvent | 2023-07-27 23:07:02 | dev-launchers/dev-launchers-platform | https://api.github.com/repos/dev-launchers/dev-launchers-platform | opened | Document Research Processes Unification Plan | UXR Universal Design | Document an outline plan for unifying research processes within Dev Launchers. The objective is to establish a roadmap and strategy for the unification initiative.
**Acceptance Criteria:**
- Determine the timeline and realistic sprint cycles for each stage of the unification process.
- Identify resources, tools, and training needs to support the unification efforts.
- Document the outline plan with clear action items and deliverables. | 1.0 | Document Research Processes Unification Plan - Document an outline plan for unifying research processes within Dev Launchers. The objective is to establish a roadmap and strategy for the unification initiative.
**Acceptance Criteria:**
- Determine the timeline and realistic sprint cycles for each stage of the unification process.
- Identify resources, tools, and training needs to support the unification efforts.
- Document the outline plan with clear action items and deliverables. | non_priority | document research processes unification plan document an outline plan for unifying research processes within dev launchers the objective is to establish a roadmap and strategy for the unification initiative acceptance criteria determine the timeline and realistic sprint cycles for each stage of the unification process identify resources tools and training needs to support the unification efforts document the outline plan with clear action items and deliverables | 0 |
40,493 | 5,223,914,091 | IssuesEvent | 2017-01-27 13:59:16 | sps-it15/dnd | https://api.github.com/repos/sps-it15/dnd | reopened | Svět | game design idea | Nápady na svět:
# Složení
## Ostrovy
Největší oblasti na mapě by mohly být ostrovy nebo kontinenty. Velikost kolem 4-5 krajů.
## Kraje
Kraje, státy, království. Každé obývané jinou rasou nebo stejnou ale ne vedle dalšího se stejnou a navíc s jiným přátelským statusem. Velikost kolem 5 - 10 prostředí.
## Prostředí
Každý Kraj by měl 5 - 10 (~8) prostředí (= les, louka, hory atd.). Prostředí by se skládala z 1 - 5 (~3) Oblastí.
## Oblast
Zobrazovaná část mapy (údolí, zátoka, les). Zobrazení jako seznam možných cílů nebo jako jednoduchá mapa ???. Velikost kolem 10 míst.
## Místo
Město, mítina, brod, okolí samostané budovy (srubu v horách). Zobrazení jako malá mapa nebo jako seznam věcí se kterými se dá něco dělat ???.
## Budova
Vnitřek jedné budovy. Zobrazení jako malá mapa nebo jako seznam věcí se kterými se dá něco dělat ???.
Celkem by na jeden ostrov vycházelo **200 - 2 500** míst. Možná je to na jednoho hráče trochu moc, #2.
# Události
## Simulace
Všechny události ve světě by se "simulovat" i když u nich nikdo není, aby svět nepůsobil prázdně. Otázka je jak dlouhý by měl být jeden den. Hlasování je [tady](http://poll.lab.io/2r-gmlcnE1QWzma7SCFV2A). | 1.0 | Svět - Nápady na svět:
# Složení
## Ostrovy
Největší oblasti na mapě by mohly být ostrovy nebo kontinenty. Velikost kolem 4-5 krajů.
## Kraje
Kraje, státy, království. Každé obývané jinou rasou nebo stejnou ale ne vedle dalšího se stejnou a navíc s jiným přátelským statusem. Velikost kolem 5 - 10 prostředí.
## Prostředí
Každý Kraj by měl 5 - 10 (~8) prostředí (= les, louka, hory atd.). Prostředí by se skládala z 1 - 5 (~3) Oblastí.
## Oblast
Zobrazovaná část mapy (údolí, zátoka, les). Zobrazení jako seznam možných cílů nebo jako jednoduchá mapa ???. Velikost kolem 10 míst.
## Místo
Město, mítina, brod, okolí samostané budovy (srubu v horách). Zobrazení jako malá mapa nebo jako seznam věcí se kterými se dá něco dělat ???.
## Budova
Vnitřek jedné budovy. Zobrazení jako malá mapa nebo jako seznam věcí se kterými se dá něco dělat ???.
Celkem by na jeden ostrov vycházelo **200 - 2 500** míst. Možná je to na jednoho hráče trochu moc, #2.
# Události
## Simulace
Všechny události ve světě by se "simulovat" i když u nich nikdo není, aby svět nepůsobil prázdně. Otázka je jak dlouhý by měl být jeden den. Hlasování je [tady](http://poll.lab.io/2r-gmlcnE1QWzma7SCFV2A). | non_priority | svět nápady na svět složení ostrovy největší oblasti na mapě by mohly být ostrovy nebo kontinenty velikost kolem krajů kraje kraje státy království každé obývané jinou rasou nebo stejnou ale ne vedle dalšího se stejnou a navíc s jiným přátelským statusem velikost kolem prostředí prostředí každý kraj by měl prostředí les louka hory atd prostředí by se skládala z oblastí oblast zobrazovaná část mapy údolí zátoka les zobrazení jako seznam možných cílů nebo jako jednoduchá mapa velikost kolem míst místo město mítina brod okolí samostané budovy srubu v horách zobrazení jako malá mapa nebo jako seznam věcí se kterými se dá něco dělat budova vnitřek jedné budovy zobrazení jako malá mapa nebo jako seznam věcí se kterými se dá něco dělat celkem by na jeden ostrov vycházelo míst možná je to na jednoho hráče trochu moc události simulace všechny události ve světě by se simulovat i když u nich nikdo není aby svět nepůsobil prázdně otázka je jak dlouhý by měl být jeden den hlasování je | 0 |
4,537 | 7,191,374,112 | IssuesEvent | 2018-02-02 20:46:13 | TakeTenGaming/DatMod | https://api.github.com/repos/TakeTenGaming/DatMod | reopened | Add "The One Probe" Support | Compatibility | Even though I don't currently have any items that can actually use *The One Probe* to display anything, I would like to eventually add a compatibility class for it to ensure when I do add items/blocks that can utilize it it's there. | True | Add "The One Probe" Support - Even though I don't currently have any items that can actually use *The One Probe* to display anything, I would like to eventually add a compatibility class for it to ensure when I do add items/blocks that can utilize it it's there. | non_priority | add the one probe support even though i don t currently have any items that can actually use the one probe to display anything i would like to eventually add a compatibility class for it to ensure when i do add items blocks that can utilize it it s there | 0 |
222,287 | 24,697,484,079 | IssuesEvent | 2022-10-19 13:10:16 | cherryrm/ytmdesktop | https://api.github.com/repos/cherryrm/ytmdesktop | opened | CVE-2022-3517 (High) detected in minimatch-3.0.4.tgz | security vulnerability | ## CVE-2022-3517 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimatch-3.0.4.tgz</b></p></summary>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimatch/-/minimatch-3.0.4.tgz">https://registry.npmjs.org/minimatch/-/minimatch-3.0.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npx/node_modules/npm/node_modules/glob/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- electron-builder-22.7.0.tgz (Root Library)
- app-builder-lib-22.7.0.tgz
- :x: **minimatch-3.0.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/cherryrm/ytmdesktop/git/commits/4bd10865d46496ece49e5ae9a473afe63e6c218c">4bd10865d46496ece49e5ae9a473afe63e6c218c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A vulnerability was found in the minimatch package. This flaw allows a Regular Expression Denial of Service (ReDoS) when calling the braceExpand function with specific arguments, resulting in a Denial of Service.
<p>Publish Date: 2022-10-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-3517>CVE-2022-3517</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-17</p>
<p>Fix Resolution: minimatch - 3.0.5</p>
</p>
</details>
<p></p>
| True | CVE-2022-3517 (High) detected in minimatch-3.0.4.tgz - ## CVE-2022-3517 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimatch-3.0.4.tgz</b></p></summary>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimatch/-/minimatch-3.0.4.tgz">https://registry.npmjs.org/minimatch/-/minimatch-3.0.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npx/node_modules/npm/node_modules/glob/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- electron-builder-22.7.0.tgz (Root Library)
- app-builder-lib-22.7.0.tgz
- :x: **minimatch-3.0.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/cherryrm/ytmdesktop/git/commits/4bd10865d46496ece49e5ae9a473afe63e6c218c">4bd10865d46496ece49e5ae9a473afe63e6c218c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A vulnerability was found in the minimatch package. This flaw allows a Regular Expression Denial of Service (ReDoS) when calling the braceExpand function with specific arguments, resulting in a Denial of Service.
<p>Publish Date: 2022-10-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-3517>CVE-2022-3517</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-17</p>
<p>Fix Resolution: minimatch - 3.0.5</p>
</p>
</details>
<p></p>
| non_priority | cve high detected in minimatch tgz cve high severity vulnerability vulnerable library minimatch tgz a glob matcher in javascript library home page a href path to dependency file package json path to vulnerable library node modules npx node modules npm node modules glob node modules minimatch package json dependency hierarchy electron builder tgz root library app builder lib tgz x minimatch tgz vulnerable library found in head commit a href found in base branch master vulnerability details a vulnerability was found in the minimatch package this flaw allows a regular expression denial of service redos when calling the braceexpand function with specific arguments resulting in a denial of service publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution minimatch | 0 |
41,649 | 5,383,041,001 | IssuesEvent | 2017-02-24 04:29:59 | randoop/randoop | https://api.github.com/repos/randoop/randoop | closed | Flaky tests when --repeat-heuristic=true | flaky tests | Randoop classifies a test sequence as "flaky" whenever an exception is thrown by a statement other than the last statement of the sequence. This is based on the standard construction of sequences that implies that any statement prior to the last is from a sequence that has already executed normally. However, when `--repeat-heuristic=true`, a new sequence has a suffix consisting of a repeated new statement. In this case, a failure within this suffix is not flaky behavior. (Observation from test ForwardExplorerTests2 that generates sequences calling a nonterminating method.)
| 1.0 | Flaky tests when --repeat-heuristic=true - Randoop classifies a test sequence as "flaky" whenever an exception is thrown by a statement other than the last statement of the sequence. This is based on the standard construction of sequences that implies that any statement prior to the last is from a sequence that has already executed normally. However, when `--repeat-heuristic=true`, a new sequence has a suffix consisting of a repeated new statement. In this case, a failure within this suffix is not flaky behavior. (Observation from test ForwardExplorerTests2 that generates sequences calling a nonterminating method.)
| non_priority | flaky tests when repeat heuristic true randoop classifies a test sequence as flaky whenever an exception is thrown by a statement other than the last statement of the sequence this is based on the standard construction of sequences that implies that any statement prior to the last is from a sequence that has already executed normally however when repeat heuristic true a new sequence has a suffix consisting of a repeated new statement in this case a failure within this suffix is not flaky behavior observation from test that generates sequences calling a nonterminating method | 0 |
95,855 | 10,894,835,067 | IssuesEvent | 2019-11-19 09:30:00 | restic/restic | https://api.github.com/repos/restic/restic | closed | Encryption documentation very hidden | documentation enhancement feedback needed | I looked at this project for the first time and it was hard to find the encryption details, which is something I always look at in such a kind of projects.
## Actual behavior
I finally found it in the references doc with the search funtcion, but that was hard. On the intro page it just mentions that it dopes it "safely". That is okay to day, but it does not mean anything. As a user I want to see facts.
<!--
In this section, please try to concentrate on observations, so only describe
what you observed directly.
-->
## Expected behaviour
It should mention AES on the first page, already. Details maybe somewhere more obvious, e.g. on the "Encryption" doc page.
<!--
The more time you spend describing an easy way to reproduce the behavior (if
this is possible), the easier it is for the project developers to fix it!
-->
| 1.0 | Encryption documentation very hidden - I looked at this project for the first time and it was hard to find the encryption details, which is something I always look at in such a kind of projects.
## Actual behavior
I finally found it in the references doc with the search funtcion, but that was hard. On the intro page it just mentions that it dopes it "safely". That is okay to day, but it does not mean anything. As a user I want to see facts.
<!--
In this section, please try to concentrate on observations, so only describe
what you observed directly.
-->
## Expected behaviour
It should mention AES on the first page, already. Details maybe somewhere more obvious, e.g. on the "Encryption" doc page.
<!--
The more time you spend describing an easy way to reproduce the behavior (if
this is possible), the easier it is for the project developers to fix it!
-->
| non_priority | encryption documentation very hidden i looked at this project for the first time and it was hard to find the encryption details which is something i always look at in such a kind of projects actual behavior i finally found it in the references doc with the search funtcion but that was hard on the intro page it just mentions that it dopes it safely that is okay to day but it does not mean anything as a user i want to see facts in this section please try to concentrate on observations so only describe what you observed directly expected behaviour it should mention aes on the first page already details maybe somewhere more obvious e g on the encryption doc page the more time you spend describing an easy way to reproduce the behavior if this is possible the easier it is for the project developers to fix it | 0 |
99,803 | 8,711,965,824 | IssuesEvent | 2018-12-06 20:46:29 | learn-co-curriculum/orm-mapping-to-table-lab | https://api.github.com/repos/learn-co-curriculum/orm-mapping-to-table-lab | closed | Small bug in the test for Student attributes | Test | Hello. I stumbled upon a small bug in the rspec test for Student attributes. Specifically, the test labeled "has an id that is readable but not writable" passes even if I don't have an attr_reader for the "id" attribute (and if I don't have the "id" as an optional argument in #initialize). The test checks to make sure that it can't write to the instance variable "id" after initialization, but it doesn't check to see whether "id" was actually defined.
I have attached a screenshot below. Thank you for looking into this!
Sdcrouse

| 1.0 | Small bug in the test for Student attributes - Hello. I stumbled upon a small bug in the rspec test for Student attributes. Specifically, the test labeled "has an id that is readable but not writable" passes even if I don't have an attr_reader for the "id" attribute (and if I don't have the "id" as an optional argument in #initialize). The test checks to make sure that it can't write to the instance variable "id" after initialization, but it doesn't check to see whether "id" was actually defined.
I have attached a screenshot below. Thank you for looking into this!
Sdcrouse

| non_priority | small bug in the test for student attributes hello i stumbled upon a small bug in the rspec test for student attributes specifically the test labeled has an id that is readable but not writable passes even if i don t have an attr reader for the id attribute and if i don t have the id as an optional argument in initialize the test checks to make sure that it can t write to the instance variable id after initialization but it doesn t check to see whether id was actually defined i have attached a screenshot below thank you for looking into this sdcrouse | 0 |
14,829 | 4,998,429,277 | IssuesEvent | 2016-12-09 19:49:41 | VATSIM-UK/core | https://api.github.com/repos/VATSIM-UK/core | closed | ErrorException in GET /mship/auth/verify | bug bugsnag code critical in progress | ## Error in VATSIM-UK/Core
**ErrorException** in **GET /mship/auth/verify**
Argument 1 passed to App\Models\Mship\Account::addQualification() must be an instance of App\Models\Mship\Qualification, null given, called in /var/www/core/app/Http/Controllers/Mship/Authentication.php on line 206 and defined
[View on Bugsnag](https://app.bugsnag.com/vatsim-uk/vatsim-uk-slash-core/errors/584477b81e51a96a2ae82b84?event_id=584477b8f780d011000f79ce)
## Stacktrace
app/Models/Mship/Account.php:1079 - Illuminate\Foundation\Bootstrap\HandleExceptions::handleError
app/Models/Mship/Account.php:1079 - App\Models\Mship\Account::addQualification
app/Http/Controllers/Mship/Authentication.php:206 - App\Http\Controllers\Mship\Authentication::App\Http\Controllers\Mship\{closure}
app/Http/Controllers/Mship/Authentication.php:268 - Vatsim\OAuth\Facades\SSO::validate
app/Http/Controllers/Mship/Authentication.php:268 - App\Http\Controllers\Mship\Authentication::getVerify
app/Http/Controllers/BaseController.php:50 - App\Http\Controllers\BaseController::App\Http\Controllers\{closure}
app/Http/Middleware/TrackInactivity.php:41 - App\Http\Middleware\TrackInactivity::handle
[View full stacktrace](https://app.bugsnag.com/vatsim-uk/vatsim-uk-slash-core/errors/584477b81e51a96a2ae82b84?event_id=584477b8f780d011000f79ce) | 1.0 | ErrorException in GET /mship/auth/verify - ## Error in VATSIM-UK/Core
**ErrorException** in **GET /mship/auth/verify**
Argument 1 passed to App\Models\Mship\Account::addQualification() must be an instance of App\Models\Mship\Qualification, null given, called in /var/www/core/app/Http/Controllers/Mship/Authentication.php on line 206 and defined
[View on Bugsnag](https://app.bugsnag.com/vatsim-uk/vatsim-uk-slash-core/errors/584477b81e51a96a2ae82b84?event_id=584477b8f780d011000f79ce)
## Stacktrace
app/Models/Mship/Account.php:1079 - Illuminate\Foundation\Bootstrap\HandleExceptions::handleError
app/Models/Mship/Account.php:1079 - App\Models\Mship\Account::addQualification
app/Http/Controllers/Mship/Authentication.php:206 - App\Http\Controllers\Mship\Authentication::App\Http\Controllers\Mship\{closure}
app/Http/Controllers/Mship/Authentication.php:268 - Vatsim\OAuth\Facades\SSO::validate
app/Http/Controllers/Mship/Authentication.php:268 - App\Http\Controllers\Mship\Authentication::getVerify
app/Http/Controllers/BaseController.php:50 - App\Http\Controllers\BaseController::App\Http\Controllers\{closure}
app/Http/Middleware/TrackInactivity.php:41 - App\Http\Middleware\TrackInactivity::handle
[View full stacktrace](https://app.bugsnag.com/vatsim-uk/vatsim-uk-slash-core/errors/584477b81e51a96a2ae82b84?event_id=584477b8f780d011000f79ce) | non_priority | errorexception in get mship auth verify error in vatsim uk core errorexception in get mship auth verify argument passed to app models mship account addqualification must be an instance of app models mship qualification null given called in var www core app http controllers mship authentication php on line and defined stacktrace app models mship account php illuminate foundation bootstrap handleexceptions handleerror app models mship account php app models mship account addqualification app http controllers mship authentication php app http controllers mship authentication app http controllers mship closure app http controllers mship authentication php vatsim oauth facades sso validate app http controllers mship authentication php app http controllers mship authentication getverify app http controllers basecontroller php app http controllers basecontroller app http controllers closure app http middleware trackinactivity php app http middleware trackinactivity handle | 0 |
9,246 | 3,265,986,750 | IssuesEvent | 2015-10-22 18:39:10 | meetup/sassquatch2 | https://api.github.com/repos/meetup/sassquatch2 | closed | `wrapNice` documentation is wrong | Documentation | 
not even close to what this class does. probably a copy/paste error | 1.0 | `wrapNice` documentation is wrong - 
not even close to what this class does. probably a copy/paste error | non_priority | wrapnice documentation is wrong not even close to what this class does probably a copy paste error | 0 |
67,656 | 7,056,629,889 | IssuesEvent | 2018-01-04 13:35:04 | sudar/bulk-delete | https://api.github.com/repos/sudar/bulk-delete | closed | Setup tests | in progress tests | Setup unit tests
- [x] Run wp-cli command to setup scaffolding
- [x] Setup Travis
- [x] Setup code coverage in Scrutinizer
- [x] Add Sample tests
| 1.0 | Setup tests - Setup unit tests
- [x] Run wp-cli command to setup scaffolding
- [x] Setup Travis
- [x] Setup code coverage in Scrutinizer
- [x] Add Sample tests
| non_priority | setup tests setup unit tests run wp cli command to setup scaffolding setup travis setup code coverage in scrutinizer add sample tests | 0 |
87,228 | 17,191,741,315 | IssuesEvent | 2021-07-16 12:01:51 | eclipse-theia/theia | https://api.github.com/repos/eclipse-theia/theia | closed | Upgrade VSCode API version | vscode | <!-- Please fill out the following content for a feature request. -->
Currently the version of VS Code API is 1.50.0 which is defined as [VSCODE_DEFAULT_API_VERSION](https://github.com/eclipse-theia/theia/blob/c92e822830e356c77d3186fda73b47f91da272e9/packages/plugin-ext-vscode/src/common/plugin-vscode-types.ts#L17)
Many of vscode extensions require VS Code API version > 1.50.0, here is a list of some of them:
- [vscode-go](https://github.com/golang/vscode-go/) -> 1.52.0
- [vscode-yaml ](https://github.com/redhat-developer/vscode-yaml) -> 1.52.0
- [vscode-java](https://github.com/redhat-developer/vscode-java) -> 1.53.2
To use these extensions with Theia we need to update that value. Some of API is not implemented in Theia but after upgrading it would be a better chance to add that missed API. For example @tsmaeder has already done some investigation what is missing for vscode-java extension: https://github.com/eclipse/che/issues/20134#issuecomment-880542184
<!-- Please provide a clear description of the feature and any relevant information. -->
### Feature Description:
Update VSCODE_DEFAULT_API_VERSION at least to 1.52.0 | 1.0 | Upgrade VSCode API version - <!-- Please fill out the following content for a feature request. -->
Currently the version of VS Code API is 1.50.0 which is defined as [VSCODE_DEFAULT_API_VERSION](https://github.com/eclipse-theia/theia/blob/c92e822830e356c77d3186fda73b47f91da272e9/packages/plugin-ext-vscode/src/common/plugin-vscode-types.ts#L17)
Many of vscode extensions require VS Code API version > 1.50.0, here is a list of some of them:
- [vscode-go](https://github.com/golang/vscode-go/) -> 1.52.0
- [vscode-yaml ](https://github.com/redhat-developer/vscode-yaml) -> 1.52.0
- [vscode-java](https://github.com/redhat-developer/vscode-java) -> 1.53.2
To use these extensions with Theia we need to update that value. Some of API is not implemented in Theia but after upgrading it would be a better chance to add that missed API. For example @tsmaeder has already done some investigation what is missing for vscode-java extension: https://github.com/eclipse/che/issues/20134#issuecomment-880542184
<!-- Please provide a clear description of the feature and any relevant information. -->
### Feature Description:
Update VSCODE_DEFAULT_API_VERSION at least to 1.52.0 | non_priority | upgrade vscode api version currently the version of vs code api is which is defined as many of vscode extensions require vs code api version here is a list of some of them to use these extensions with theia we need to update that value some of api is not implemented in theia but after upgrading it would be a better chance to add that missed api for example tsmaeder has already done some investigation what is missing for vscode java extension feature description update vscode default api version at least to | 0 |
79,770 | 10,141,726,837 | IssuesEvent | 2019-08-03 16:49:31 | hexpm/hex | https://api.github.com/repos/hexpm/hex | closed | 8MB tarball size limit | Kind:Documentation Note:Discussion | I could not find the documentation regarding this limit anywhere -- I had to dig into the erlang source code to find out about this limit. Perhaps it would be good to document this somewhere.
Also, is there any possibility that this limit will be raised in the future?
Currently I am building a pure Elixir interface to the WordNet lexical/semantic database, similar to Ruby's `rwordnet`. I want to bundle the database directly with the package, but right now I need to compress the dataset in a `.tar.xz` so that it can fit under the 8MB tarball limit, while on rubygems, the limit is higher so `rwordnet` can just include the datasets uncompressed. I would really love to be able to remove the dependency on `tar` and `xz`. | 1.0 | 8MB tarball size limit - I could not find the documentation regarding this limit anywhere -- I had to dig into the erlang source code to find out about this limit. Perhaps it would be good to document this somewhere.
Also, is there any possibility that this limit will be raised in the future?
Currently I am building a pure Elixir interface to the WordNet lexical/semantic database, similar to Ruby's `rwordnet`. I want to bundle the database directly with the package, but right now I need to compress the dataset in a `.tar.xz` so that it can fit under the 8MB tarball limit, while on rubygems, the limit is higher so `rwordnet` can just include the datasets uncompressed. I would really love to be able to remove the dependency on `tar` and `xz`. | non_priority | tarball size limit i could not find the documentation regarding this limit anywhere i had to dig into the erlang source code to find out about this limit perhaps it would be good to document this somewhere also is there any possibility that this limit will be raised in the future currently i am building a pure elixir interface to the wordnet lexical semantic database similar to ruby s rwordnet i want to bundle the database directly with the package but right now i need to compress the dataset in a tar xz so that it can fit under the tarball limit while on rubygems the limit is higher so rwordnet can just include the datasets uncompressed i would really love to be able to remove the dependency on tar and xz | 0 |
116,761 | 14,998,699,441 | IssuesEvent | 2021-01-29 18:50:58 | vmware/clarity | https://api.github.com/repos/vmware/clarity | closed | Wizard header area and footer border enhancement | Dev resolution: best with core type: design type: enhancement | <!--
PLEASE FILL OUT THE FOLLOWING. WE MAY CLOSE INCOMPLETE ISSUES.
-->
**Select one ...** (check one with "x")
```
[ ] bug
[ ] feature request
[x] enhancement
```
### Description
Enhancements to the wizard structure and hierarchy.
- Header area
- Footer border
### Documentation
Enhancement to the wizard structure to allow for a top level header area that is separated by a horizontal rule. Header spacing maintains standard 24px padding with the added horizontal rule at the bottom of the header area. Add a horizontal rule to separate the wizard controls in the footer area from the rest of the wizard content. Footer spacing maintains 24px padding and placement within wizard content area with horizontal rule at the top of the footer area. See specs below:
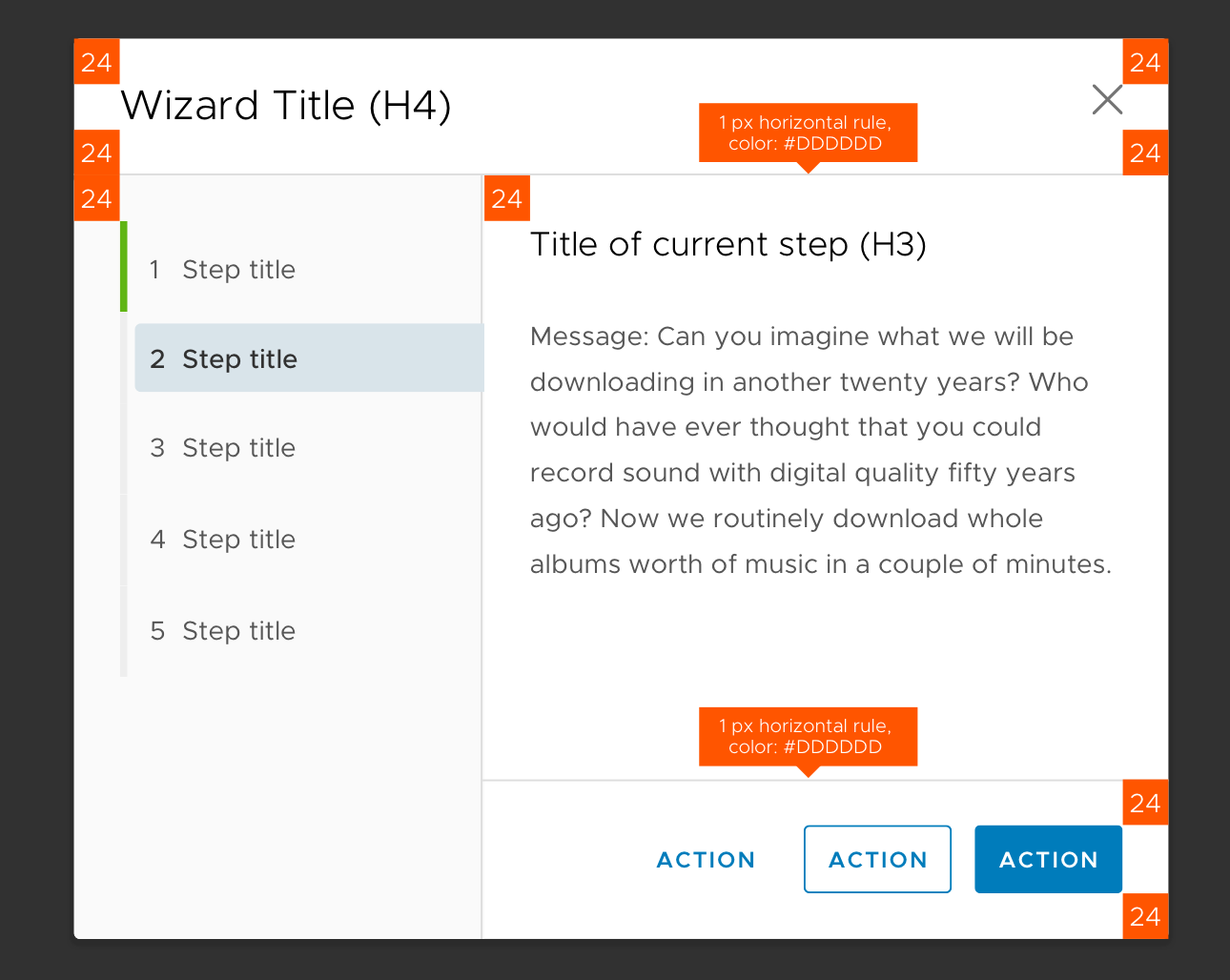
| 1.0 | Wizard header area and footer border enhancement - <!--
PLEASE FILL OUT THE FOLLOWING. WE MAY CLOSE INCOMPLETE ISSUES.
-->
**Select one ...** (check one with "x")
```
[ ] bug
[ ] feature request
[x] enhancement
```
### Description
Enhancements to the wizard structure and hierarchy.
- Header area
- Footer border
### Documentation
Enhancement to the wizard structure to allow for a top level header area that is separated by a horizontal rule. Header spacing maintains standard 24px padding with the added horizontal rule at the bottom of the header area. Add a horizontal rule to separate the wizard controls in the footer area from the rest of the wizard content. Footer spacing maintains 24px padding and placement within wizard content area with horizontal rule at the top of the footer area. See specs below:
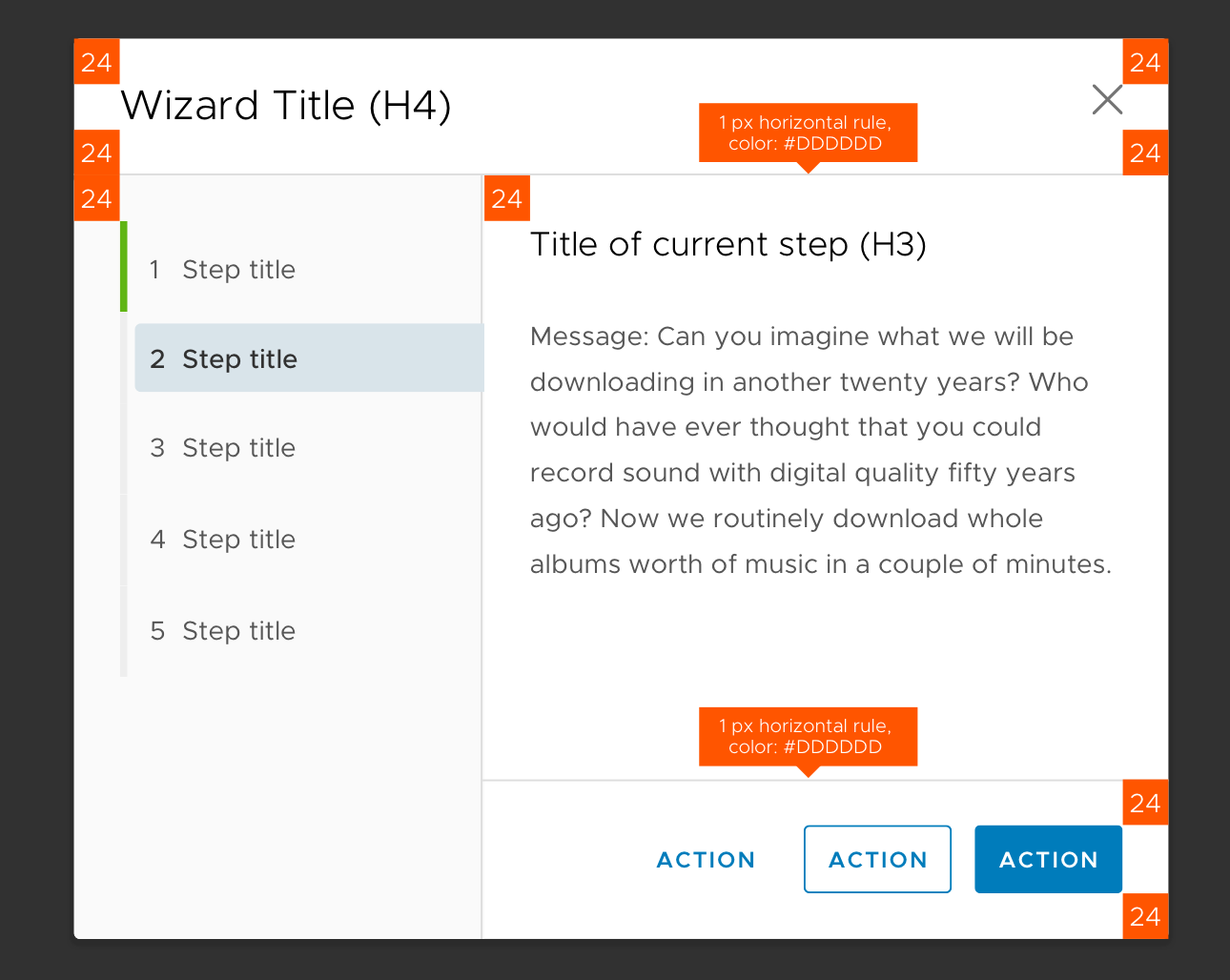
| non_priority | wizard header area and footer border enhancement please fill out the following we may close incomplete issues select one check one with x bug feature request enhancement description enhancements to the wizard structure and hierarchy header area footer border documentation enhancement to the wizard structure to allow for a top level header area that is separated by a horizontal rule header spacing maintains standard padding with the added horizontal rule at the bottom of the header area add a horizontal rule to separate the wizard controls in the footer area from the rest of the wizard content footer spacing maintains padding and placement within wizard content area with horizontal rule at the top of the footer area see specs below | 0 |
117,523 | 11,948,938,110 | IssuesEvent | 2020-04-03 12:49:23 | Hogfeldt/transcov | https://api.github.com/repos/Hogfeldt/transcov | closed | Add auto directive for API module | documentation | Make the docstrings from the API module available in the API documentation | 1.0 | Add auto directive for API module - Make the docstrings from the API module available in the API documentation | non_priority | add auto directive for api module make the docstrings from the api module available in the api documentation | 0 |
30,649 | 11,842,013,568 | IssuesEvent | 2020-03-23 22:01:10 | Mohib-hub/karate | https://api.github.com/repos/Mohib-hub/karate | opened | CVE-2019-11272 (High) detected in spring-security-core-4.2.2.RELEASE.jar | security vulnerability | ## CVE-2019-11272 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-security-core-4.2.2.RELEASE.jar</b></p></summary>
<p>spring-security-core</p>
<p>Library home page: <a href="http://spring.io/spring-security">http://spring.io/spring-security</a></p>
<p>Path to dependency file: /tmp/ws-scm/karate/karate-demo/build.gradle</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/org.springframework.security/spring-security-core/4.2.2.RELEASE/b4797b71d9f7d1a4b76b5d095ac20868369a8c31/spring-security-core-4.2.2.RELEASE.jar,/root/.gradle/caches/modules-2/files-2.1/org.springframework.security/spring-security-core/4.2.2.RELEASE/b4797b71d9f7d1a4b76b5d095ac20868369a8c31/spring-security-core-4.2.2.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-security-1.5.3.RELEASE.jar (Root Library)
- spring-security-web-4.2.2.RELEASE.jar
- :x: **spring-security-core-4.2.2.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Mohib-hub/karate/commit/c8766c8277306046ef9c6f01148b98b0d2bafe02">c8766c8277306046ef9c6f01148b98b0d2bafe02</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Security, versions 4.2.x up to 4.2.12, and older unsupported versions support plain text passwords using PlaintextPasswordEncoder. If an application using an affected version of Spring Security is leveraging PlaintextPasswordEncoder and a user has a null encoded password, a malicious user (or attacker) can authenticate using a password of "null".
<p>Publish Date: 2019-06-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11272>CVE-2019-11272</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11272">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11272</a></p>
<p>Release Date: 2019-06-26</p>
<p>Fix Resolution: org.springframework.security:spring-security-core:4.2.13.RELEASE</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework.security","packageName":"spring-security-core","packageVersion":"4.2.2.RELEASE","isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-security:1.5.3.RELEASE;org.springframework.security:spring-security-web:4.2.2.RELEASE;org.springframework.security:spring-security-core:4.2.2.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework.security:spring-security-core:4.2.13.RELEASE"}],"vulnerabilityIdentifier":"CVE-2019-11272","vulnerabilityDetails":"Spring Security, versions 4.2.x up to 4.2.12, and older unsupported versions support plain text passwords using PlaintextPasswordEncoder. If an application using an affected version of Spring Security is leveraging PlaintextPasswordEncoder and a user has a null encoded password, a malicious user (or attacker) can authenticate using a password of \"null\".","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11272","cvss3Severity":"high","cvss3Score":"7.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2019-11272 (High) detected in spring-security-core-4.2.2.RELEASE.jar - ## CVE-2019-11272 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-security-core-4.2.2.RELEASE.jar</b></p></summary>
<p>spring-security-core</p>
<p>Library home page: <a href="http://spring.io/spring-security">http://spring.io/spring-security</a></p>
<p>Path to dependency file: /tmp/ws-scm/karate/karate-demo/build.gradle</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/org.springframework.security/spring-security-core/4.2.2.RELEASE/b4797b71d9f7d1a4b76b5d095ac20868369a8c31/spring-security-core-4.2.2.RELEASE.jar,/root/.gradle/caches/modules-2/files-2.1/org.springframework.security/spring-security-core/4.2.2.RELEASE/b4797b71d9f7d1a4b76b5d095ac20868369a8c31/spring-security-core-4.2.2.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-security-1.5.3.RELEASE.jar (Root Library)
- spring-security-web-4.2.2.RELEASE.jar
- :x: **spring-security-core-4.2.2.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Mohib-hub/karate/commit/c8766c8277306046ef9c6f01148b98b0d2bafe02">c8766c8277306046ef9c6f01148b98b0d2bafe02</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Security, versions 4.2.x up to 4.2.12, and older unsupported versions support plain text passwords using PlaintextPasswordEncoder. If an application using an affected version of Spring Security is leveraging PlaintextPasswordEncoder and a user has a null encoded password, a malicious user (or attacker) can authenticate using a password of "null".
<p>Publish Date: 2019-06-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11272>CVE-2019-11272</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11272">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11272</a></p>
<p>Release Date: 2019-06-26</p>
<p>Fix Resolution: org.springframework.security:spring-security-core:4.2.13.RELEASE</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework.security","packageName":"spring-security-core","packageVersion":"4.2.2.RELEASE","isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-security:1.5.3.RELEASE;org.springframework.security:spring-security-web:4.2.2.RELEASE;org.springframework.security:spring-security-core:4.2.2.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework.security:spring-security-core:4.2.13.RELEASE"}],"vulnerabilityIdentifier":"CVE-2019-11272","vulnerabilityDetails":"Spring Security, versions 4.2.x up to 4.2.12, and older unsupported versions support plain text passwords using PlaintextPasswordEncoder. If an application using an affected version of Spring Security is leveraging PlaintextPasswordEncoder and a user has a null encoded password, a malicious user (or attacker) can authenticate using a password of \"null\".","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11272","cvss3Severity":"high","cvss3Score":"7.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in spring security core release jar cve high severity vulnerability vulnerable library spring security core release jar spring security core library home page a href path to dependency file tmp ws scm karate karate demo build gradle path to vulnerable library root gradle caches modules files org springframework security spring security core release spring security core release jar root gradle caches modules files org springframework security spring security core release spring security core release jar dependency hierarchy spring boot starter security release jar root library spring security web release jar x spring security core release jar vulnerable library found in head commit a href vulnerability details spring security versions x up to and older unsupported versions support plain text passwords using plaintextpasswordencoder if an application using an affected version of spring security is leveraging plaintextpasswordencoder and a user has a null encoded password a malicious user or attacker can authenticate using a password of null publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework security spring security core release isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails spring security versions x up to and older unsupported versions support plain text passwords using plaintextpasswordencoder if an application using an affected version of spring security is leveraging plaintextpasswordencoder and a user has a null encoded password a malicious user or attacker can authenticate using a password of null vulnerabilityurl | 0 |
186,734 | 15,082,363,251 | IssuesEvent | 2021-02-05 14:28:47 | Lookyloo/lookyloo | https://api.github.com/repos/Lookyloo/lookyloo | closed | Help or Q&A section in menu | UI Improvements documentation good first issue | ## Describe the change
*(A clear and concise description of what you want to happen)*
Currently there is no any help section nor Q&A section in the main menu.
## How will this impact users?
Would give the users more information on what they can do with Lookyloo.
## To which release does this apply?
- [] Current release
- [] Future release
## Additional context
*(Add any other context or screenshots about the feature request here)*
1.
1.
1.
| 1.0 | Help or Q&A section in menu - ## Describe the change
*(A clear and concise description of what you want to happen)*
Currently there is no any help section nor Q&A section in the main menu.
## How will this impact users?
Would give the users more information on what they can do with Lookyloo.
## To which release does this apply?
- [] Current release
- [] Future release
## Additional context
*(Add any other context or screenshots about the feature request here)*
1.
1.
1.
| non_priority | help or q a section in menu describe the change a clear and concise description of what you want to happen currently there is no any help section nor q a section in the main menu how will this impact users would give the users more information on what they can do with lookyloo to which release does this apply current release future release additional context add any other context or screenshots about the feature request here | 0 |
72,127 | 8,705,282,118 | IssuesEvent | 2018-12-05 21:55:20 | swentel/indigenous-android | https://api.github.com/repos/swentel/indigenous-android | opened | Add a 'compact' mode and full detail activity per post | Design Usability | The timeline is sometimes too large imo, making it compact might be more interesting in some cases.
Related with #127 - when there's a dedicated activity then, we don't need to 'fix' the read more.
And it gives us more screen estate to print all relevant data.
In this case, it might be handy then to slide from one post to another though, with the context also if the next post is still new or not | 1.0 | Add a 'compact' mode and full detail activity per post - The timeline is sometimes too large imo, making it compact might be more interesting in some cases.
Related with #127 - when there's a dedicated activity then, we don't need to 'fix' the read more.
And it gives us more screen estate to print all relevant data.
In this case, it might be handy then to slide from one post to another though, with the context also if the next post is still new or not | non_priority | add a compact mode and full detail activity per post the timeline is sometimes too large imo making it compact might be more interesting in some cases related with when there s a dedicated activity then we don t need to fix the read more and it gives us more screen estate to print all relevant data in this case it might be handy then to slide from one post to another though with the context also if the next post is still new or not | 0 |
112,215 | 9,557,911,695 | IssuesEvent | 2019-05-03 12:58:58 | medic/medic-release-testing | https://api.github.com/repos/medic/medic-release-testing | closed | Add a new language and ensure the app functions correctly. | Chrome Desktop Release Test | User: Restricted User
Site: Standard Config
Platform: Desktop With Chrome
Test Steps:
As an admin add a new custom language to the application.
Log in as a restricted user that has the custom language as there language.
Ensure the app loads. EX: Tasks are showing, targets are calculating, reports are visible, and people are enabled. | 1.0 | Add a new language and ensure the app functions correctly. - User: Restricted User
Site: Standard Config
Platform: Desktop With Chrome
Test Steps:
As an admin add a new custom language to the application.
Log in as a restricted user that has the custom language as there language.
Ensure the app loads. EX: Tasks are showing, targets are calculating, reports are visible, and people are enabled. | non_priority | add a new language and ensure the app functions correctly user restricted user site standard config platform desktop with chrome test steps as an admin add a new custom language to the application log in as a restricted user that has the custom language as there language ensure the app loads ex tasks are showing targets are calculating reports are visible and people are enabled | 0 |
258,065 | 22,274,458,203 | IssuesEvent | 2022-06-10 15:14:44 | mautic/mautic | https://api.github.com/repos/mautic/mautic | closed | In SchemaException.php line 34: [Doctrine\DBAL\Schema\SchemaException (10)] There is no table with name 'mautic_leads' in the schema. | bug ready-to-test | ### Mautic Version
4.2.x series
### PHP version
7.4.26
### What browsers are you seeing the problem on?
Microsoft Edge
### What happened?
M 4.3.1
When I tried install custom objects plugin I see this info:
```
In SchemaException.php line 34:
[Doctrine\DBAL\Schema\SchemaException (10)]
There is no table with name 'mautic_pr.pressleads' in the schema.
Exception trace:
at /var/www/pr/vendor/doctrine/dbal/lib/Doctrine/DBAL/Schema/SchemaException.php:34
Doctrine\DBAL\Schema\SchemaException::tableDoesNotExist() at /var/www/pr/vendor/doctrine/dbal/lib/Doctrine/DBAL/Schema/Schema.php:178
Doctrine\DBAL\Schema\Schema->getTable() at /var/www/pr/app/bundles/InstallBundle/EventListener/DoctrineEventSubscriber.php:28
Mautic\InstallBundle\EventListener\DoctrineEventSubscriber->postGenerateSchema() at /var/www/pr/vendor/symfony/doctrine-bridge/ContainerAwareEventManager.php:64
Symfony\Bridge\Doctrine\ContainerAwareEventManager->dispatchEvent() at /var/www/pr/vendor/doctrine/orm/lib/Doctrine/ORM/Tools/SchemaTool.php:409
Doctrine\ORM\Tools\SchemaTool->getSchemaFromMetadata() at /var/www/pr/vendor/doctrine/orm/lib/Doctrine/ORM/Tools/SchemaTool.php:116
Doctrine\ORM\Tools\SchemaTool->getCreateSchemaSql() at /var/www/pr/app/bundles/PluginBundle/Bundle/PluginBundleBase.php:47
Mautic\PluginBundle\Bundle\PluginBundleBase::installPluginSchema() at /var/www/pr/app/bundles/PluginBundle/Bundle/PluginBundleBase.php:27
Mautic\PluginBundle\Bundle\PluginBundleBase::onPluginInstall() at /var/www/pr/plugins/MauticRefreshSegmentButtonPluginBundle/MauticRefreshSegmentButtonPluginBundle.php:28
MauticPlugin\MauticRefreshSegmentButtonPluginBundle\MauticRefreshSegmentButtonPluginBundle::onPluginInstall() at /var/www/pr/app/bundles/PluginBundle/Helper/ReloadHelper.php:133
Mautic\PluginBundle\Helper\ReloadHelper->installPlugins() at /var/www/pr/app/bundles/PluginBundle/Facade/ReloadFacade.php:40
Mautic\PluginBundle\Facade\ReloadFacade->reloadPlugins() at /var/www/pr/app/bundles/PluginBundle/Command/ReloadCommand.php:35
Mautic\PluginBundle\Command\ReloadCommand->execute() at /var/www/pr/vendor/symfony/console/Command/Command.php:255
Symfony\Component\Console\Command\Command->run() at /var/www/pr/vendor/symfony/console/Application.php:1027
Symfony\Component\Console\Application->doRunCommand() at /var/www/pr/vendor/symfony/framework-bundle/Console/Application.php:97
Symfony\Bundle\FrameworkBundle\Console\Application->doRunCommand() at /var/www/pr/vendor/symfony/console/Application.php:273
Symfony\Component\Console\Application->doRun() at /var/www/pr/vendor/symfony/framework-bundle/Console/Application.php:83
Symfony\Bundle\FrameworkBundle\Console\Application->doRun() at /var/www/pr/vendor/symfony/console/Application.php:149
Symfony\Component\Console\Application->run() at /var/www/pr/bin/console:42
mautic:plugins:reload [-h|--help] [-q|--quiet] [-v|vv|vvv|--verbose] [-V|--version] [--ansi] [--no-ansi] [-n|--no-interaction] [-e|--env ENV] [--no-debug] [--] <command>
```
`
It looks similar to: https://github.com/mautic/mautic/issues/11163
### How can we reproduce this issue?
Step 1: Upload custom objects budle
Step 2: Run mautic:plugins:reload -vvv
### Relevant log output
```shell
In SchemaException.php line 34:
[Doctrine\DBAL\Schema\SchemaException (10)]
There is no table with name 'mautic_pr.pressleads' in the schema.
Exception trace:
at /var/www/pr/vendor/doctrine/dbal/lib/Doctrine/DBAL/Schema/SchemaException.php:34
Doctrine\DBAL\Schema\SchemaException::tableDoesNotExist() at /var/www/pr/vendor/doctrine/dbal/lib/Doctrine/DBAL/Schema/Schema.php:178
Doctrine\DBAL\Schema\Schema->getTable() at /var/www/pr/app/bundles/InstallBundle/EventListener/DoctrineEventSubscriber.php:28
Mautic\InstallBundle\EventListener\DoctrineEventSubscriber->postGenerateSchema() at /var/www/pr/vendor/symfony/doctrine-bridge/ContainerAwareEventManager.php:64
Symfony\Bridge\Doctrine\ContainerAwareEventManager->dispatchEvent() at /var/www/pr/vendor/doctrine/orm/lib/Doctrine/ORM/Tools/SchemaTool.php:409
Doctrine\ORM\Tools\SchemaTool->getSchemaFromMetadata() at /var/www/pr/vendor/doctrine/orm/lib/Doctrine/ORM/Tools/SchemaTool.php:116
Doctrine\ORM\Tools\SchemaTool->getCreateSchemaSql() at /var/www/pr/app/bundles/PluginBundle/Bundle/PluginBundleBase.php:47
Mautic\PluginBundle\Bundle\PluginBundleBase::installPluginSchema() at /var/www/pr/app/bundles/PluginBundle/Bundle/PluginBundleBase.php:27
Mautic\PluginBundle\Bundle\PluginBundleBase::onPluginInstall() at /var/www/pr/plugins/MauticRefreshSegmentButtonPluginBundle/MauticRefreshSegmentButtonPluginBundle.php:28
MauticPlugin\MauticRefreshSegmentButtonPluginBundle\MauticRefreshSegmentButtonPluginBundle::onPluginInstall() at /var/www/pr/app/bundles/PluginBundle/Helper/ReloadHelper.php:133
Mautic\PluginBundle\Helper\ReloadHelper->installPlugins() at /var/www/pr/app/bundles/PluginBundle/Facade/ReloadFacade.php:40
Mautic\PluginBundle\Facade\ReloadFacade->reloadPlugins() at /var/www/pr/app/bundles/PluginBundle/Command/ReloadCommand.php:35
Mautic\PluginBundle\Command\ReloadCommand->execute() at /var/www/pr/vendor/symfony/console/Command/Command.php:255
Symfony\Component\Console\Command\Command->run() at /var/www/pr/vendor/symfony/console/Application.php:1027
Symfony\Component\Console\Application->doRunCommand() at /var/www/pr/vendor/symfony/framework-bundle/Console/Application.php:97
Symfony\Bundle\FrameworkBundle\Console\Application->doRunCommand() at /var/www/pr/vendor/symfony/console/Application.php:273
Symfony\Component\Console\Application->doRun() at /var/www/pr/vendor/symfony/framework-bundle/Console/Application.php:83
Symfony\Bundle\FrameworkBundle\Console\Application->doRun() at /var/www/pr/vendor/symfony/console/Application.php:149
Symfony\Component\Console\Application->run() at /var/www/pr/bin/console:42
mautic:plugins:reload [-h|--help] [-q|--quiet] [-v|vv|vvv|--verbose] [-V|--version] [--ansi] [--no-ansi] [-n|--no-interaction] [-e|--env ENV] [--no-debug] [--] <command>
```
### Code of Conduct
- [X] I confirm that I have read and agree to follow this project's Code of Conduct | 1.0 | In SchemaException.php line 34: [Doctrine\DBAL\Schema\SchemaException (10)] There is no table with name 'mautic_leads' in the schema. - ### Mautic Version
4.2.x series
### PHP version
7.4.26
### What browsers are you seeing the problem on?
Microsoft Edge
### What happened?
M 4.3.1
When I tried install custom objects plugin I see this info:
```
In SchemaException.php line 34:
[Doctrine\DBAL\Schema\SchemaException (10)]
There is no table with name 'mautic_pr.pressleads' in the schema.
Exception trace:
at /var/www/pr/vendor/doctrine/dbal/lib/Doctrine/DBAL/Schema/SchemaException.php:34
Doctrine\DBAL\Schema\SchemaException::tableDoesNotExist() at /var/www/pr/vendor/doctrine/dbal/lib/Doctrine/DBAL/Schema/Schema.php:178
Doctrine\DBAL\Schema\Schema->getTable() at /var/www/pr/app/bundles/InstallBundle/EventListener/DoctrineEventSubscriber.php:28
Mautic\InstallBundle\EventListener\DoctrineEventSubscriber->postGenerateSchema() at /var/www/pr/vendor/symfony/doctrine-bridge/ContainerAwareEventManager.php:64
Symfony\Bridge\Doctrine\ContainerAwareEventManager->dispatchEvent() at /var/www/pr/vendor/doctrine/orm/lib/Doctrine/ORM/Tools/SchemaTool.php:409
Doctrine\ORM\Tools\SchemaTool->getSchemaFromMetadata() at /var/www/pr/vendor/doctrine/orm/lib/Doctrine/ORM/Tools/SchemaTool.php:116
Doctrine\ORM\Tools\SchemaTool->getCreateSchemaSql() at /var/www/pr/app/bundles/PluginBundle/Bundle/PluginBundleBase.php:47
Mautic\PluginBundle\Bundle\PluginBundleBase::installPluginSchema() at /var/www/pr/app/bundles/PluginBundle/Bundle/PluginBundleBase.php:27
Mautic\PluginBundle\Bundle\PluginBundleBase::onPluginInstall() at /var/www/pr/plugins/MauticRefreshSegmentButtonPluginBundle/MauticRefreshSegmentButtonPluginBundle.php:28
MauticPlugin\MauticRefreshSegmentButtonPluginBundle\MauticRefreshSegmentButtonPluginBundle::onPluginInstall() at /var/www/pr/app/bundles/PluginBundle/Helper/ReloadHelper.php:133
Mautic\PluginBundle\Helper\ReloadHelper->installPlugins() at /var/www/pr/app/bundles/PluginBundle/Facade/ReloadFacade.php:40
Mautic\PluginBundle\Facade\ReloadFacade->reloadPlugins() at /var/www/pr/app/bundles/PluginBundle/Command/ReloadCommand.php:35
Mautic\PluginBundle\Command\ReloadCommand->execute() at /var/www/pr/vendor/symfony/console/Command/Command.php:255
Symfony\Component\Console\Command\Command->run() at /var/www/pr/vendor/symfony/console/Application.php:1027
Symfony\Component\Console\Application->doRunCommand() at /var/www/pr/vendor/symfony/framework-bundle/Console/Application.php:97
Symfony\Bundle\FrameworkBundle\Console\Application->doRunCommand() at /var/www/pr/vendor/symfony/console/Application.php:273
Symfony\Component\Console\Application->doRun() at /var/www/pr/vendor/symfony/framework-bundle/Console/Application.php:83
Symfony\Bundle\FrameworkBundle\Console\Application->doRun() at /var/www/pr/vendor/symfony/console/Application.php:149
Symfony\Component\Console\Application->run() at /var/www/pr/bin/console:42
mautic:plugins:reload [-h|--help] [-q|--quiet] [-v|vv|vvv|--verbose] [-V|--version] [--ansi] [--no-ansi] [-n|--no-interaction] [-e|--env ENV] [--no-debug] [--] <command>
```
`
It looks similar to: https://github.com/mautic/mautic/issues/11163
### How can we reproduce this issue?
Step 1: Upload custom objects budle
Step 2: Run mautic:plugins:reload -vvv
### Relevant log output
```shell
In SchemaException.php line 34:
[Doctrine\DBAL\Schema\SchemaException (10)]
There is no table with name 'mautic_pr.pressleads' in the schema.
Exception trace:
at /var/www/pr/vendor/doctrine/dbal/lib/Doctrine/DBAL/Schema/SchemaException.php:34
Doctrine\DBAL\Schema\SchemaException::tableDoesNotExist() at /var/www/pr/vendor/doctrine/dbal/lib/Doctrine/DBAL/Schema/Schema.php:178
Doctrine\DBAL\Schema\Schema->getTable() at /var/www/pr/app/bundles/InstallBundle/EventListener/DoctrineEventSubscriber.php:28
Mautic\InstallBundle\EventListener\DoctrineEventSubscriber->postGenerateSchema() at /var/www/pr/vendor/symfony/doctrine-bridge/ContainerAwareEventManager.php:64
Symfony\Bridge\Doctrine\ContainerAwareEventManager->dispatchEvent() at /var/www/pr/vendor/doctrine/orm/lib/Doctrine/ORM/Tools/SchemaTool.php:409
Doctrine\ORM\Tools\SchemaTool->getSchemaFromMetadata() at /var/www/pr/vendor/doctrine/orm/lib/Doctrine/ORM/Tools/SchemaTool.php:116
Doctrine\ORM\Tools\SchemaTool->getCreateSchemaSql() at /var/www/pr/app/bundles/PluginBundle/Bundle/PluginBundleBase.php:47
Mautic\PluginBundle\Bundle\PluginBundleBase::installPluginSchema() at /var/www/pr/app/bundles/PluginBundle/Bundle/PluginBundleBase.php:27
Mautic\PluginBundle\Bundle\PluginBundleBase::onPluginInstall() at /var/www/pr/plugins/MauticRefreshSegmentButtonPluginBundle/MauticRefreshSegmentButtonPluginBundle.php:28
MauticPlugin\MauticRefreshSegmentButtonPluginBundle\MauticRefreshSegmentButtonPluginBundle::onPluginInstall() at /var/www/pr/app/bundles/PluginBundle/Helper/ReloadHelper.php:133
Mautic\PluginBundle\Helper\ReloadHelper->installPlugins() at /var/www/pr/app/bundles/PluginBundle/Facade/ReloadFacade.php:40
Mautic\PluginBundle\Facade\ReloadFacade->reloadPlugins() at /var/www/pr/app/bundles/PluginBundle/Command/ReloadCommand.php:35
Mautic\PluginBundle\Command\ReloadCommand->execute() at /var/www/pr/vendor/symfony/console/Command/Command.php:255
Symfony\Component\Console\Command\Command->run() at /var/www/pr/vendor/symfony/console/Application.php:1027
Symfony\Component\Console\Application->doRunCommand() at /var/www/pr/vendor/symfony/framework-bundle/Console/Application.php:97
Symfony\Bundle\FrameworkBundle\Console\Application->doRunCommand() at /var/www/pr/vendor/symfony/console/Application.php:273
Symfony\Component\Console\Application->doRun() at /var/www/pr/vendor/symfony/framework-bundle/Console/Application.php:83
Symfony\Bundle\FrameworkBundle\Console\Application->doRun() at /var/www/pr/vendor/symfony/console/Application.php:149
Symfony\Component\Console\Application->run() at /var/www/pr/bin/console:42
mautic:plugins:reload [-h|--help] [-q|--quiet] [-v|vv|vvv|--verbose] [-V|--version] [--ansi] [--no-ansi] [-n|--no-interaction] [-e|--env ENV] [--no-debug] [--] <command>
```
### Code of Conduct
- [X] I confirm that I have read and agree to follow this project's Code of Conduct | non_priority | in schemaexception php line there is no table with name mautic leads in the schema mautic version x series php version what browsers are you seeing the problem on microsoft edge what happened m when i tried install custom objects plugin i see this info in schemaexception php line there is no table with name mautic pr pressleads in the schema exception trace at var www pr vendor doctrine dbal lib doctrine dbal schema schemaexception php doctrine dbal schema schemaexception tabledoesnotexist at var www pr vendor doctrine dbal lib doctrine dbal schema schema php doctrine dbal schema schema gettable at var www pr app bundles installbundle eventlistener doctrineeventsubscriber php mautic installbundle eventlistener doctrineeventsubscriber postgenerateschema at var www pr vendor symfony doctrine bridge containerawareeventmanager php symfony bridge doctrine containerawareeventmanager dispatchevent at var www pr vendor doctrine orm lib doctrine orm tools schematool php doctrine orm tools schematool getschemafrommetadata at var www pr vendor doctrine orm lib doctrine orm tools schematool php doctrine orm tools schematool getcreateschemasql at var www pr app bundles pluginbundle bundle pluginbundlebase php mautic pluginbundle bundle pluginbundlebase installpluginschema at var www pr app bundles pluginbundle bundle pluginbundlebase php mautic pluginbundle bundle pluginbundlebase onplugininstall at var www pr plugins mauticrefreshsegmentbuttonpluginbundle mauticrefreshsegmentbuttonpluginbundle php mauticplugin mauticrefreshsegmentbuttonpluginbundle mauticrefreshsegmentbuttonpluginbundle onplugininstall at var www pr app bundles pluginbundle helper reloadhelper php mautic pluginbundle helper reloadhelper installplugins at var www pr app bundles pluginbundle facade reloadfacade php mautic pluginbundle facade reloadfacade reloadplugins at var www pr app bundles pluginbundle command reloadcommand php mautic pluginbundle command reloadcommand execute at var www pr vendor symfony console command command php symfony component console command command run at var www pr vendor symfony console application php symfony component console application doruncommand at var www pr vendor symfony framework bundle console application php symfony bundle frameworkbundle console application doruncommand at var www pr vendor symfony console application php symfony component console application dorun at var www pr vendor symfony framework bundle console application php symfony bundle frameworkbundle console application dorun at var www pr vendor symfony console application php symfony component console application run at var www pr bin console mautic plugins reload it looks similar to how can we reproduce this issue step upload custom objects budle step run mautic plugins reload vvv relevant log output shell in schemaexception php line there is no table with name mautic pr pressleads in the schema exception trace at var www pr vendor doctrine dbal lib doctrine dbal schema schemaexception php doctrine dbal schema schemaexception tabledoesnotexist at var www pr vendor doctrine dbal lib doctrine dbal schema schema php doctrine dbal schema schema gettable at var www pr app bundles installbundle eventlistener doctrineeventsubscriber php mautic installbundle eventlistener doctrineeventsubscriber postgenerateschema at var www pr vendor symfony doctrine bridge containerawareeventmanager php symfony bridge doctrine containerawareeventmanager dispatchevent at var www pr vendor doctrine orm lib doctrine orm tools schematool php doctrine orm tools schematool getschemafrommetadata at var www pr vendor doctrine orm lib doctrine orm tools schematool php doctrine orm tools schematool getcreateschemasql at var www pr app bundles pluginbundle bundle pluginbundlebase php mautic pluginbundle bundle pluginbundlebase installpluginschema at var www pr app bundles pluginbundle bundle pluginbundlebase php mautic pluginbundle bundle pluginbundlebase onplugininstall at var www pr plugins mauticrefreshsegmentbuttonpluginbundle mauticrefreshsegmentbuttonpluginbundle php mauticplugin mauticrefreshsegmentbuttonpluginbundle mauticrefreshsegmentbuttonpluginbundle onplugininstall at var www pr app bundles pluginbundle helper reloadhelper php mautic pluginbundle helper reloadhelper installplugins at var www pr app bundles pluginbundle facade reloadfacade php mautic pluginbundle facade reloadfacade reloadplugins at var www pr app bundles pluginbundle command reloadcommand php mautic pluginbundle command reloadcommand execute at var www pr vendor symfony console command command php symfony component console command command run at var www pr vendor symfony console application php symfony component console application doruncommand at var www pr vendor symfony framework bundle console application php symfony bundle frameworkbundle console application doruncommand at var www pr vendor symfony console application php symfony component console application dorun at var www pr vendor symfony framework bundle console application php symfony bundle frameworkbundle console application dorun at var www pr vendor symfony console application php symfony component console application run at var www pr bin console mautic plugins reload code of conduct i confirm that i have read and agree to follow this project s code of conduct | 0 |
121,480 | 12,127,158,394 | IssuesEvent | 2020-04-22 18:14:35 | aces/Loris | https://api.github.com/repos/aces/Loris | closed | [media] Update test plan to remove mention of "site" field | 23.0.0-testing Bug Critical to release Documentation | **Describe the bug**
The site selection has been removed in https://github.com/aces/Loris/pull/5577 but the test plan was never updated. | 1.0 | [media] Update test plan to remove mention of "site" field - **Describe the bug**
The site selection has been removed in https://github.com/aces/Loris/pull/5577 but the test plan was never updated. | non_priority | update test plan to remove mention of site field describe the bug the site selection has been removed in but the test plan was never updated | 0 |
5,220 | 8,017,742,859 | IssuesEvent | 2018-07-25 16:50:37 | DynareTeam/dynare | https://api.github.com/repos/DynareTeam/dynare | closed | Preprocessor: Support creating empty arrays with [] (wishlist) | enhancement preprocessor | It would be great if [] returned an empty array. (At the moment it produces an error.) Doing [ "" ] - [ "" ] is a bit cumbersome!
| 1.0 | Preprocessor: Support creating empty arrays with [] (wishlist) - It would be great if [] returned an empty array. (At the moment it produces an error.) Doing [ "" ] - [ "" ] is a bit cumbersome!
| non_priority | preprocessor support creating empty arrays with wishlist it would be great if returned an empty array at the moment it produces an error doing is a bit cumbersome | 0 |
81,034 | 10,221,067,258 | IssuesEvent | 2019-08-15 23:46:48 | gatsbyjs/gatsby | https://api.github.com/repos/gatsbyjs/gatsby | closed | [docs] add info about working with multiple images | effort: med help wanted impact: high not stale topic: images/media type: documentation | ## Summary
As part of the [image workflow evaluation](https://github.com/gatsbyjs/gatsby/issues/14529), one use case that would be good to document is how to work with multiple images, like with an image gallery or something. Currently options are somewhat limited and the GraphQL workflow is awkward, but hopefully that will be improved in the future with https://github.com/gatsbyjs/gatsby/issues/10482.
In order to keep the overarching image workflow evaluation issue from depending on this one item, I've created this new issue to track the need for docs on working with multiple images.
Here's an example of how they are referenced in the current docs for [Working With Images](https://www.gatsbyjs.org/docs/working-with-images/), in the section on fragments:
```
export const query = graphql`
query {
image1: file(relativePath: { eq: "images/image1.jpg" }) {
...squareImage
}
image2: file(relativePath: { eq: "images/image2.jpg" }) {
...squareImage
}
image3: file(relativePath: { eq: "images/image3.jpg" }) {
...squareImage
}
}
```
This is very repetitive...and for anything more than a handful of images it's quite awkward. We're open to any ideas for making this more dynamic, while keeping in mind that https://github.com/gatsbyjs/gatsby/issues/10482 is likely the ultimate direction. | 1.0 | [docs] add info about working with multiple images - ## Summary
As part of the [image workflow evaluation](https://github.com/gatsbyjs/gatsby/issues/14529), one use case that would be good to document is how to work with multiple images, like with an image gallery or something. Currently options are somewhat limited and the GraphQL workflow is awkward, but hopefully that will be improved in the future with https://github.com/gatsbyjs/gatsby/issues/10482.
In order to keep the overarching image workflow evaluation issue from depending on this one item, I've created this new issue to track the need for docs on working with multiple images.
Here's an example of how they are referenced in the current docs for [Working With Images](https://www.gatsbyjs.org/docs/working-with-images/), in the section on fragments:
```
export const query = graphql`
query {
image1: file(relativePath: { eq: "images/image1.jpg" }) {
...squareImage
}
image2: file(relativePath: { eq: "images/image2.jpg" }) {
...squareImage
}
image3: file(relativePath: { eq: "images/image3.jpg" }) {
...squareImage
}
}
```
This is very repetitive...and for anything more than a handful of images it's quite awkward. We're open to any ideas for making this more dynamic, while keeping in mind that https://github.com/gatsbyjs/gatsby/issues/10482 is likely the ultimate direction. | non_priority | add info about working with multiple images summary as part of the one use case that would be good to document is how to work with multiple images like with an image gallery or something currently options are somewhat limited and the graphql workflow is awkward but hopefully that will be improved in the future with in order to keep the overarching image workflow evaluation issue from depending on this one item i ve created this new issue to track the need for docs on working with multiple images here s an example of how they are referenced in the current docs for in the section on fragments export const query graphql query file relativepath eq images jpg squareimage file relativepath eq images jpg squareimage file relativepath eq images jpg squareimage this is very repetitive and for anything more than a handful of images it s quite awkward we re open to any ideas for making this more dynamic while keeping in mind that is likely the ultimate direction | 0 |
2,407 | 25,177,690,776 | IssuesEvent | 2022-11-11 10:44:53 | camunda/zeebe | https://api.github.com/repos/camunda/zeebe | closed | All partitions become followers | kind/bug blocker/info area/reliability | **Describe the bug**
All of a sudden all the partitions become followers,
➜ ~ zbctl status --insecure
Cluster size: 3
Partitions count: 3
Replication factor: 3
Gateway version: 1.1.0
Brokers:
Broker 0 - zeebe-cluster-zeebe-0.zeebe-cluster-zeebe.services-1.svc.cluster.local:26501
Version: 1.1.0
Partition 1 : Follower, Healthy
Partition 2 : Follower, Healthy
Partition 3 : Follower, Healthy
Broker 1 - zeebe-cluster-zeebe-1.zeebe-cluster-zeebe.services-1.svc.cluster.local:26501
Version: 1.1.0
Partition 1 : Follower, Healthy
Partition 2 : Follower, Healthy
Partition 3 : Follower, Healthy
Broker 2 - zeebe-cluster-zeebe-2.zeebe-cluster-zeebe.services-1.svc.cluster.local:26501
Version: 1.1.0
Partition 1 : Follower, Healthy
Partition 2 : Follower, Healthy
Partition 3 : Follower, Healthy
When we restart all the pods, 3 partitions become leader, (After restart)
➜ ~ zbctl status --insecure
Cluster size: 3
Partitions count: 3
Replication factor: 3
Gateway version: 1.1.0
Brokers:
Broker 0 - zeebe-cluster-zeebe-0.zeebe-cluster-zeebe.services-1.svc.cluster.local:26501
Version: 1.1.0
Partition 1 : Leader, Healthy
Partition 2 : Leader, Healthy
Partition 3 : Follower, Healthy
Broker 1 - zeebe-cluster-zeebe-1.zeebe-cluster-zeebe.services-1.svc.cluster.local:26501
Version: 1.1.0
Partition 1 : Follower, Healthy
Partition 2 : Follower, Healthy
Partition 3 : Follower, Healthy
Broker 2 - zeebe-cluster-zeebe-2.zeebe-cluster-zeebe.services-1.svc.cluster.local:26501
Version: 1.1.0
Partition 1 : Follower, Healthy
Partition 2 : Follower, Healthy
Partition 3 : Leader, Healthy
**To Reproduce**
<!--
Steps to reproduce the behavior
If possible add a minimal reproducer code sample
- when using the Java client: https://github.com/zeebe-io/zeebe-test-template-java
-->
**Expected behavior**
There always should be 3 leaders with the current setup
**Log/Stacktrace**
<!-- If possible add the full stacktrace or Zeebe log which contains the issue. -->
<details><summary>Full Stacktrace</summary>
<p>
```
<STACKTRACE>
```
</p>
</details>
**Environment:**
- OS: Linux
- Zeebe Version: 1.1.0
- Configuration: 3 nodes statefulset on k8s cluster
| True | All partitions become followers - **Describe the bug**
All of a sudden all the partitions become followers,
➜ ~ zbctl status --insecure
Cluster size: 3
Partitions count: 3
Replication factor: 3
Gateway version: 1.1.0
Brokers:
Broker 0 - zeebe-cluster-zeebe-0.zeebe-cluster-zeebe.services-1.svc.cluster.local:26501
Version: 1.1.0
Partition 1 : Follower, Healthy
Partition 2 : Follower, Healthy
Partition 3 : Follower, Healthy
Broker 1 - zeebe-cluster-zeebe-1.zeebe-cluster-zeebe.services-1.svc.cluster.local:26501
Version: 1.1.0
Partition 1 : Follower, Healthy
Partition 2 : Follower, Healthy
Partition 3 : Follower, Healthy
Broker 2 - zeebe-cluster-zeebe-2.zeebe-cluster-zeebe.services-1.svc.cluster.local:26501
Version: 1.1.0
Partition 1 : Follower, Healthy
Partition 2 : Follower, Healthy
Partition 3 : Follower, Healthy
When we restart all the pods, 3 partitions become leader, (After restart)
➜ ~ zbctl status --insecure
Cluster size: 3
Partitions count: 3
Replication factor: 3
Gateway version: 1.1.0
Brokers:
Broker 0 - zeebe-cluster-zeebe-0.zeebe-cluster-zeebe.services-1.svc.cluster.local:26501
Version: 1.1.0
Partition 1 : Leader, Healthy
Partition 2 : Leader, Healthy
Partition 3 : Follower, Healthy
Broker 1 - zeebe-cluster-zeebe-1.zeebe-cluster-zeebe.services-1.svc.cluster.local:26501
Version: 1.1.0
Partition 1 : Follower, Healthy
Partition 2 : Follower, Healthy
Partition 3 : Follower, Healthy
Broker 2 - zeebe-cluster-zeebe-2.zeebe-cluster-zeebe.services-1.svc.cluster.local:26501
Version: 1.1.0
Partition 1 : Follower, Healthy
Partition 2 : Follower, Healthy
Partition 3 : Leader, Healthy
**To Reproduce**
<!--
Steps to reproduce the behavior
If possible add a minimal reproducer code sample
- when using the Java client: https://github.com/zeebe-io/zeebe-test-template-java
-->
**Expected behavior**
There always should be 3 leaders with the current setup
**Log/Stacktrace**
<!-- If possible add the full stacktrace or Zeebe log which contains the issue. -->
<details><summary>Full Stacktrace</summary>
<p>
```
<STACKTRACE>
```
</p>
</details>
**Environment:**
- OS: Linux
- Zeebe Version: 1.1.0
- Configuration: 3 nodes statefulset on k8s cluster
| non_priority | all partitions become followers describe the bug all of a sudden all the partitions become followers ➜ zbctl status insecure cluster size partitions count replication factor gateway version brokers broker zeebe cluster zeebe zeebe cluster zeebe services svc cluster local version partition follower healthy partition follower healthy partition follower healthy broker zeebe cluster zeebe zeebe cluster zeebe services svc cluster local version partition follower healthy partition follower healthy partition follower healthy broker zeebe cluster zeebe zeebe cluster zeebe services svc cluster local version partition follower healthy partition follower healthy partition follower healthy when we restart all the pods partitions become leader after restart ➜ zbctl status insecure cluster size partitions count replication factor gateway version brokers broker zeebe cluster zeebe zeebe cluster zeebe services svc cluster local version partition leader healthy partition leader healthy partition follower healthy broker zeebe cluster zeebe zeebe cluster zeebe services svc cluster local version partition follower healthy partition follower healthy partition follower healthy broker zeebe cluster zeebe zeebe cluster zeebe services svc cluster local version partition follower healthy partition follower healthy partition leader healthy to reproduce steps to reproduce the behavior if possible add a minimal reproducer code sample when using the java client expected behavior there always should be leaders with the current setup log stacktrace full stacktrace environment os linux zeebe version configuration nodes statefulset on cluster | 0 |
196,486 | 15,596,306,181 | IssuesEvent | 2021-03-18 15:44:03 | openintegrationhub/openintegrationhub.github.io | https://api.github.com/repos/openintegrationhub/openintegrationhub.github.io | closed | Improve Example Flows in Deployment Guidelines | deployment documentation | The deployment guides are meant to help with an initial test setup of the Open Integration Hub currently do not provide ideal test flow scenarios. We already made some changes to the [local guide ](https://github.com/openintegrationhub/openintegrationhub.github.io/blob/master/docs/3%20-%20Deployment/GCPInstallationGuide.md) to have an example with two code components. The [GCP guide ](https://github.com/openintegrationhub/openintegrationhub.github.io/blob/master/docs/3%20-%20Deployment/GCPInstallationGuide.md) still provides an older example. The flow example should be the same and but also generally updated.
We need to provide more documentation and explanation, as well as check and change what images we use for the installation setups. Components have to be compatible with recent changes and should be provided under openintegrationhub github org / dockerhub and not other partners. | 1.0 | Improve Example Flows in Deployment Guidelines - The deployment guides are meant to help with an initial test setup of the Open Integration Hub currently do not provide ideal test flow scenarios. We already made some changes to the [local guide ](https://github.com/openintegrationhub/openintegrationhub.github.io/blob/master/docs/3%20-%20Deployment/GCPInstallationGuide.md) to have an example with two code components. The [GCP guide ](https://github.com/openintegrationhub/openintegrationhub.github.io/blob/master/docs/3%20-%20Deployment/GCPInstallationGuide.md) still provides an older example. The flow example should be the same and but also generally updated.
We need to provide more documentation and explanation, as well as check and change what images we use for the installation setups. Components have to be compatible with recent changes and should be provided under openintegrationhub github org / dockerhub and not other partners. | non_priority | improve example flows in deployment guidelines the deployment guides are meant to help with an initial test setup of the open integration hub currently do not provide ideal test flow scenarios we already made some changes to the to have an example with two code components the still provides an older example the flow example should be the same and but also generally updated we need to provide more documentation and explanation as well as check and change what images we use for the installation setups components have to be compatible with recent changes and should be provided under openintegrationhub github org dockerhub and not other partners | 0 |
41,181 | 5,342,735,026 | IssuesEvent | 2017-02-17 09:11:50 | mautic/mautic | https://api.github.com/repos/mautic/mautic | closed | [Feature] Count selected leads on lists | Feature Request Ready To Test | I don't know if already has some way to see it but I couldn't find.. It would be great when we check leads in a list, Mautic show the number of leads selected.
I'm not a developer so don't know the complexity, but something simple like on excel will certainly do the trick: selecting the checkbox of the lead the counting will appear on the end of the list, maybe next to the max number of exibition on page.
| 1.0 | [Feature] Count selected leads on lists - I don't know if already has some way to see it but I couldn't find.. It would be great when we check leads in a list, Mautic show the number of leads selected.
I'm not a developer so don't know the complexity, but something simple like on excel will certainly do the trick: selecting the checkbox of the lead the counting will appear on the end of the list, maybe next to the max number of exibition on page.
| non_priority | count selected leads on lists i don t know if already has some way to see it but i couldn t find it would be great when we check leads in a list mautic show the number of leads selected i m not a developer so don t know the complexity but something simple like on excel will certainly do the trick selecting the checkbox of the lead the counting will appear on the end of the list maybe next to the max number of exibition on page | 0 |
16,725 | 21,886,178,748 | IssuesEvent | 2022-05-19 18:53:30 | qgis/QGIS | https://api.github.com/repos/qgis/QGIS | closed | Iterating over features in processing algorithm not creating correct destination folder | Processing Bug | ### What is the bug or the crash?
If there is an algorithm that takes input `QgsProcessingParameterFeatureSource` and output is `QgsProcessingParameterFolderDestination`. The `QgsProcessingParameterFolderDestination` will not be created correctly if the iterate over features button is selected.
This bug is only occurring when you provide a directory path. Working as it should with temp directories.
See the attached screenshot when accessing the directory name using `parameterAsString`
The first run is temp directory and 2nd is actual path:

### Steps to reproduce the issue
Run the following processing script and choose the option of iterating over features and provide an actual directory path to the `Output Directory`.
```python
"""
Model exported as python.
Name : model
Group :
With QGIS : 32400
"""
from qgis.core import QgsProcessing
from qgis.core import QgsProcessingAlgorithm
from qgis.core import QgsProcessingMultiStepFeedback
from qgis.core import QgsProcessingParameterFeatureSource, QgsProcessingParameterFolderDestination
import processing
class Model(QgsProcessingAlgorithm):
def initAlgorithm(self, config=None):
self.addParameter(QgsProcessingParameterFeatureSource('iterativefeatures', 'Iterative Features', types=[QgsProcessing.TypeVectorPolygon], defaultValue=None))
self.addParameter(
QgsProcessingParameterFolderDestination(
"OutputDirectory",
"Output Directory",
createByDefault=True,
defaultValue=None,
)
)
def processAlgorithm(self, parameters, context, model_feedback):
# Use a multi-step feedback, so that individual child algorithm progress reports are adjusted for the
# overall progress through the model
feedback = QgsProcessingMultiStepFeedback(0, model_feedback)
results = {}
outputs = {}
output_dir = self.parameterAsString(parameters, "OutputDirectory", context)
feedback.pushWarning(output_dir)
return results
def name(self):
return 'model'
def displayName(self):
return 'model'
def group(self):
return ''
def groupId(self):
return ''
def createInstance(self):
return Model()
```
### Versions
3.22.4
### Supported QGIS version
- [X] I'm running a supported QGIS version according to the roadmap.
### New profile
- [X] I tried with a new QGIS profile
### Additional context
I tried `parameterAsFile` and many others ways to access the `Output Directory`, and all have the same issue. | 1.0 | Iterating over features in processing algorithm not creating correct destination folder - ### What is the bug or the crash?
If there is an algorithm that takes input `QgsProcessingParameterFeatureSource` and output is `QgsProcessingParameterFolderDestination`. The `QgsProcessingParameterFolderDestination` will not be created correctly if the iterate over features button is selected.
This bug is only occurring when you provide a directory path. Working as it should with temp directories.
See the attached screenshot when accessing the directory name using `parameterAsString`
The first run is temp directory and 2nd is actual path:

### Steps to reproduce the issue
Run the following processing script and choose the option of iterating over features and provide an actual directory path to the `Output Directory`.
```python
"""
Model exported as python.
Name : model
Group :
With QGIS : 32400
"""
from qgis.core import QgsProcessing
from qgis.core import QgsProcessingAlgorithm
from qgis.core import QgsProcessingMultiStepFeedback
from qgis.core import QgsProcessingParameterFeatureSource, QgsProcessingParameterFolderDestination
import processing
class Model(QgsProcessingAlgorithm):
def initAlgorithm(self, config=None):
self.addParameter(QgsProcessingParameterFeatureSource('iterativefeatures', 'Iterative Features', types=[QgsProcessing.TypeVectorPolygon], defaultValue=None))
self.addParameter(
QgsProcessingParameterFolderDestination(
"OutputDirectory",
"Output Directory",
createByDefault=True,
defaultValue=None,
)
)
def processAlgorithm(self, parameters, context, model_feedback):
# Use a multi-step feedback, so that individual child algorithm progress reports are adjusted for the
# overall progress through the model
feedback = QgsProcessingMultiStepFeedback(0, model_feedback)
results = {}
outputs = {}
output_dir = self.parameterAsString(parameters, "OutputDirectory", context)
feedback.pushWarning(output_dir)
return results
def name(self):
return 'model'
def displayName(self):
return 'model'
def group(self):
return ''
def groupId(self):
return ''
def createInstance(self):
return Model()
```
### Versions
3.22.4
### Supported QGIS version
- [X] I'm running a supported QGIS version according to the roadmap.
### New profile
- [X] I tried with a new QGIS profile
### Additional context
I tried `parameterAsFile` and many others ways to access the `Output Directory`, and all have the same issue. | non_priority | iterating over features in processing algorithm not creating correct destination folder what is the bug or the crash if there is an algorithm that takes input qgsprocessingparameterfeaturesource and output is qgsprocessingparameterfolderdestination the qgsprocessingparameterfolderdestination will not be created correctly if the iterate over features button is selected this bug is only occurring when you provide a directory path working as it should with temp directories see the attached screenshot when accessing the directory name using parameterasstring the first run is temp directory and is actual path steps to reproduce the issue run the following processing script and choose the option of iterating over features and provide an actual directory path to the output directory python model exported as python name model group with qgis from qgis core import qgsprocessing from qgis core import qgsprocessingalgorithm from qgis core import qgsprocessingmultistepfeedback from qgis core import qgsprocessingparameterfeaturesource qgsprocessingparameterfolderdestination import processing class model qgsprocessingalgorithm def initalgorithm self config none self addparameter qgsprocessingparameterfeaturesource iterativefeatures iterative features types defaultvalue none self addparameter qgsprocessingparameterfolderdestination outputdirectory output directory createbydefault true defaultvalue none def processalgorithm self parameters context model feedback use a multi step feedback so that individual child algorithm progress reports are adjusted for the overall progress through the model feedback qgsprocessingmultistepfeedback model feedback results outputs output dir self parameterasstring parameters outputdirectory context feedback pushwarning output dir return results def name self return model def displayname self return model def group self return def groupid self return def createinstance self return model versions supported qgis version i m running a supported qgis version according to the roadmap new profile i tried with a new qgis profile additional context i tried parameterasfile and many others ways to access the output directory and all have the same issue | 0 |
40,363 | 9,967,792,540 | IssuesEvent | 2019-07-08 14:19:16 | ShaikASK/Testing | https://api.github.com/repos/ShaikASK/Testing | opened | FF Browser : Document : Map Fields : Two Vertical Scroll bar is being displayed | Beta Release #5 Defect Document Map fields HR Admin Module HR User Module P3 | Steps To Replicate :
1.Switch to 1024 x 768 resolution
2.Launch the URL
3.Sign in HR admin user
4.Upload a document and click on save and Map fields
Experienced Behavior : Observed that two vertical scroll bar is being displayed against Map Fields screen when check with Firefox browser
Expected Behavior : Ensure that two vertical scroll bar should not be displayed against map fields screen
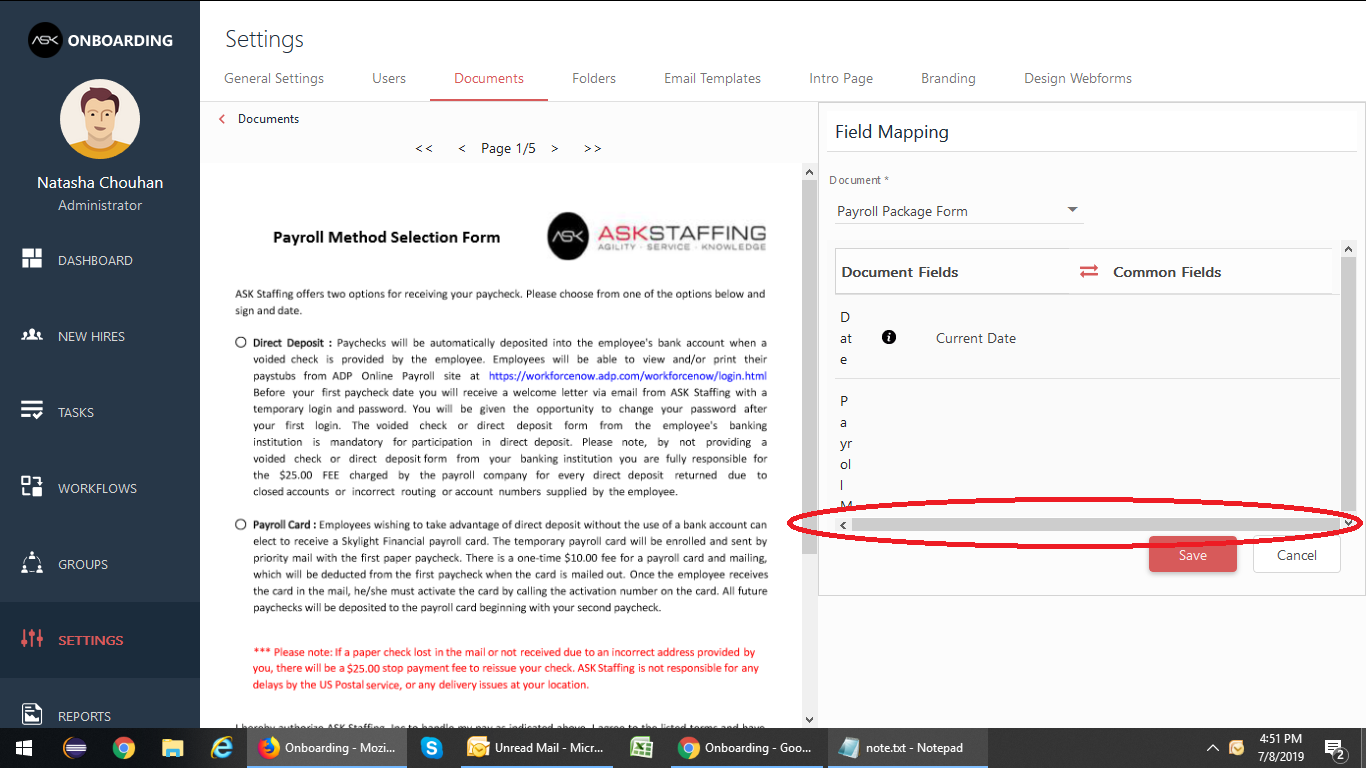
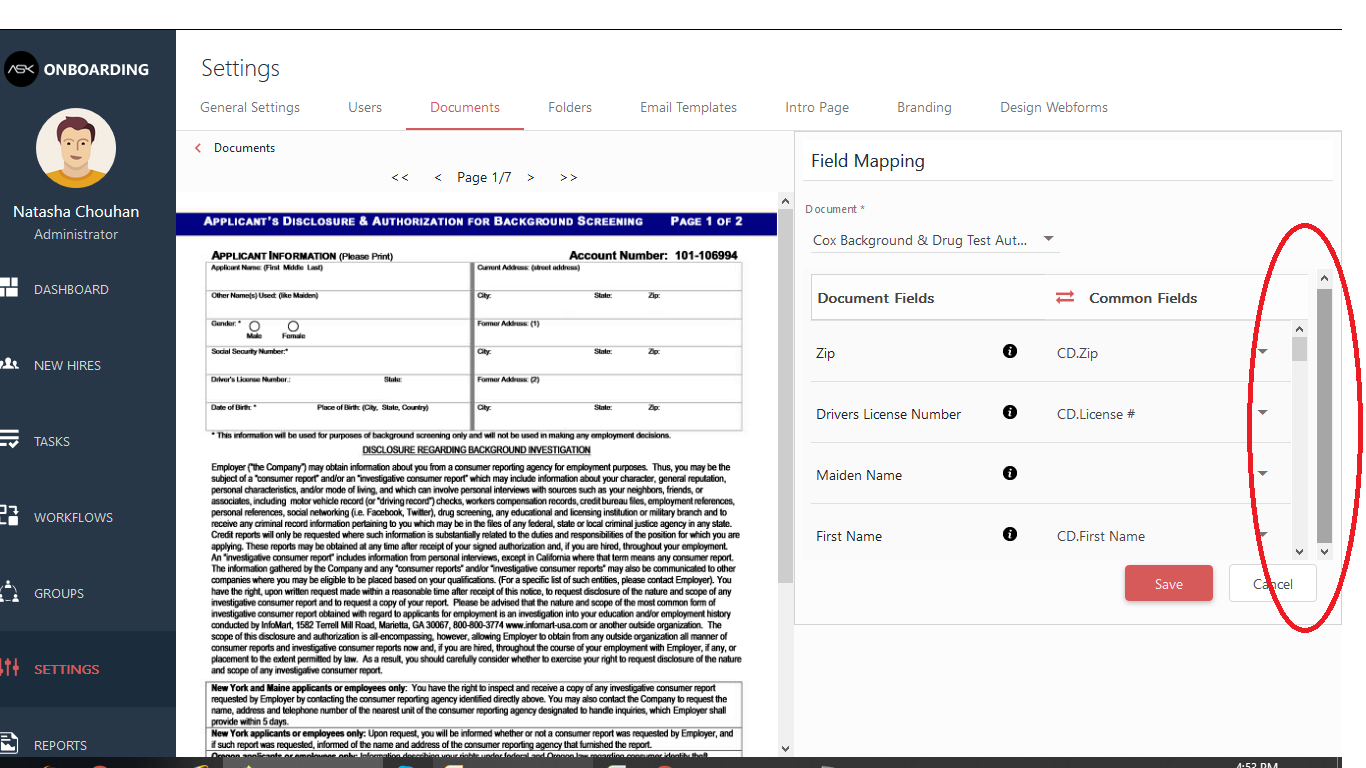
| 1.0 | FF Browser : Document : Map Fields : Two Vertical Scroll bar is being displayed - Steps To Replicate :
1.Switch to 1024 x 768 resolution
2.Launch the URL
3.Sign in HR admin user
4.Upload a document and click on save and Map fields
Experienced Behavior : Observed that two vertical scroll bar is being displayed against Map Fields screen when check with Firefox browser
Expected Behavior : Ensure that two vertical scroll bar should not be displayed against map fields screen
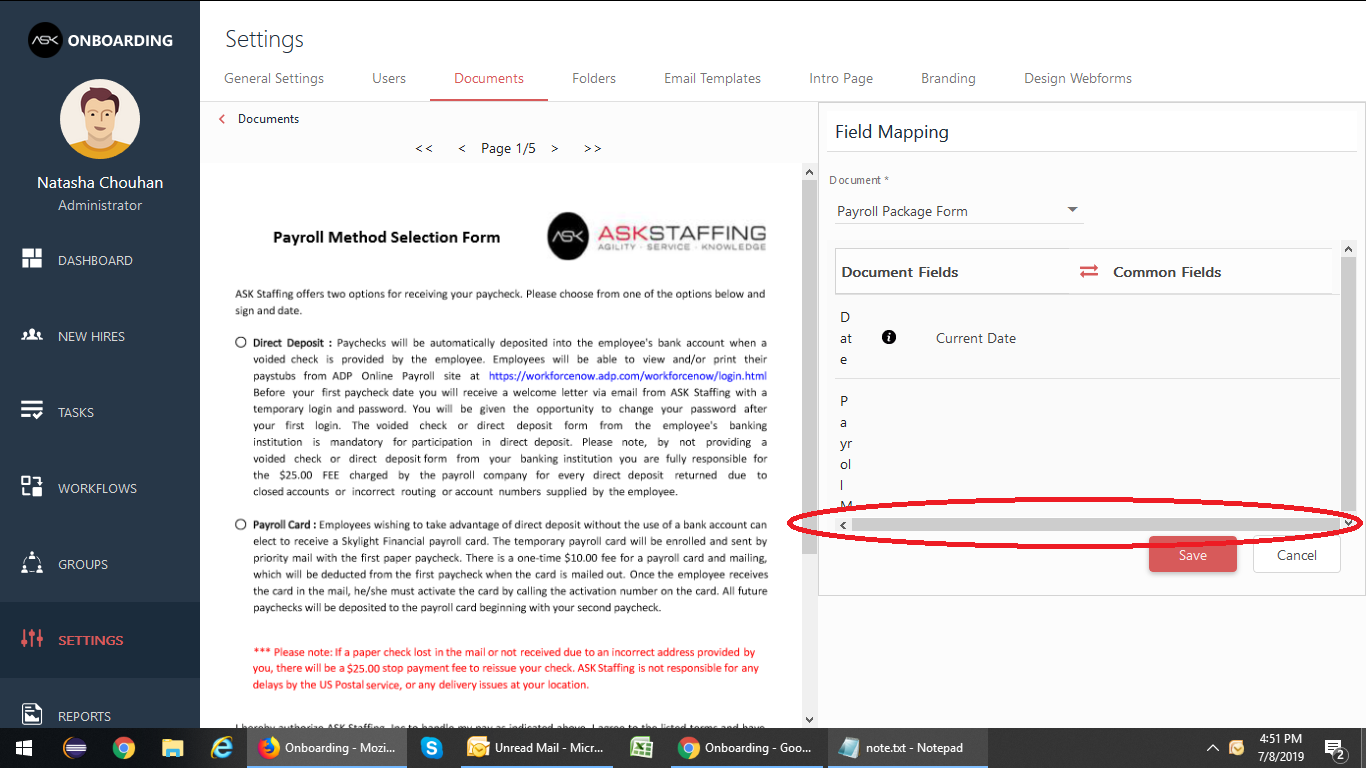
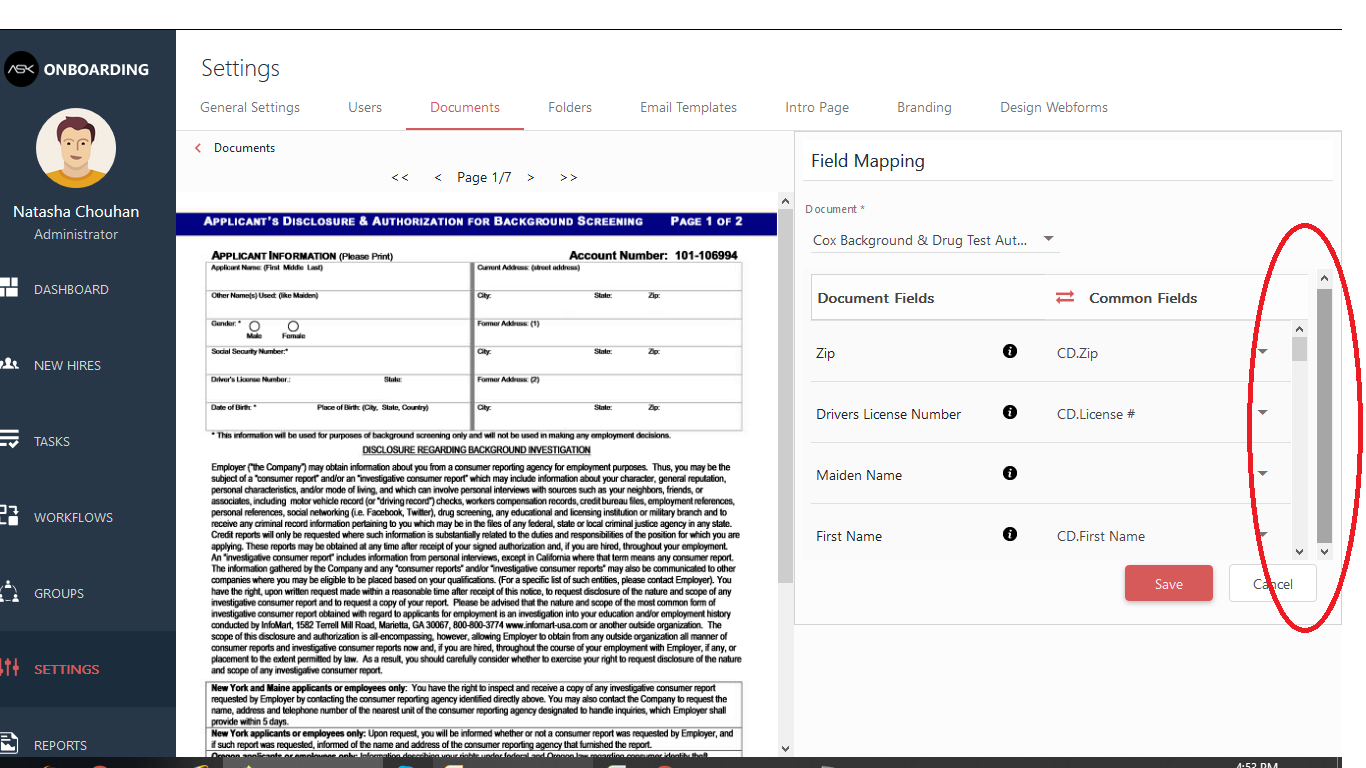
| non_priority | ff browser document map fields two vertical scroll bar is being displayed steps to replicate switch to x resolution launch the url sign in hr admin user upload a document and click on save and map fields experienced behavior observed that two vertical scroll bar is being displayed against map fields screen when check with firefox browser expected behavior ensure that two vertical scroll bar should not be displayed against map fields screen | 0 |
244,794 | 26,476,047,852 | IssuesEvent | 2023-01-17 11:12:06 | BogdanOrg/WebGoat | https://api.github.com/repos/BogdanOrg/WebGoat | closed | CVE-2016-3674 (High) detected in xstream-1.4.5.jar - autoclosed | security vulnerability | ## CVE-2016-3674 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.5.jar</b></p></summary>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>Library home page: <a href="http://codehaus.org/xstream-parent/xstream/">http://codehaus.org/xstream-parent/xstream/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/BogdanOrg/WebGoat/commit/21edcc9ab7caae616d4189d2842d5fb0ca3b91e8">21edcc9ab7caae616d4189d2842d5fb0ca3b91e8</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Multiple XML external entity (XXE) vulnerabilities in the (1) Dom4JDriver, (2) DomDriver, (3) JDomDriver, (4) JDom2Driver, (5) SjsxpDriver, (6) StandardStaxDriver, and (7) WstxDriver drivers in XStream before 1.4.9 allow remote attackers to read arbitrary files via a crafted XML document.
<p>Publish Date: 2016-05-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-3674>CVE-2016-3674</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-3674">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-3674</a></p>
<p>Release Date: 2016-05-17</p>
<p>Fix Resolution: 1.4.9</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| True | CVE-2016-3674 (High) detected in xstream-1.4.5.jar - autoclosed - ## CVE-2016-3674 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.5.jar</b></p></summary>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>Library home page: <a href="http://codehaus.org/xstream-parent/xstream/">http://codehaus.org/xstream-parent/xstream/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/BogdanOrg/WebGoat/commit/21edcc9ab7caae616d4189d2842d5fb0ca3b91e8">21edcc9ab7caae616d4189d2842d5fb0ca3b91e8</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Multiple XML external entity (XXE) vulnerabilities in the (1) Dom4JDriver, (2) DomDriver, (3) JDomDriver, (4) JDom2Driver, (5) SjsxpDriver, (6) StandardStaxDriver, and (7) WstxDriver drivers in XStream before 1.4.9 allow remote attackers to read arbitrary files via a crafted XML document.
<p>Publish Date: 2016-05-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-3674>CVE-2016-3674</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-3674">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-3674</a></p>
<p>Release Date: 2016-05-17</p>
<p>Fix Resolution: 1.4.9</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| non_priority | cve high detected in xstream jar autoclosed cve high severity vulnerability vulnerable library xstream jar xstream is a serialization library from java objects to xml and back library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository com thoughtworks xstream xstream xstream jar dependency hierarchy x xstream jar vulnerable library found in head commit a href found in base branch develop vulnerability details multiple xml external entity xxe vulnerabilities in the domdriver jdomdriver sjsxpdriver standardstaxdriver and wstxdriver drivers in xstream before allow remote attackers to read arbitrary files via a crafted xml document publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution check this box to open an automated fix pr | 0 |
91,675 | 10,726,211,256 | IssuesEvent | 2019-10-28 08:52:56 | rust-lang/rust-clippy | https://api.github.com/repos/rust-lang/rust-clippy | opened | Lint docs: Deprecated lints don't expand | L-bug :beetle: L-documentation L-website good first issue | <!--
Hi there! Whether you've come to make a suggestion for a new lint, an improvement to an existing lint or to report a bug or a false positive in Clippy, you've come to the right place.
For bug reports and false positives, please include the output of `cargo clippy -V` in the report.
Thank you for using Clippy!
Write your comment below this line: -->
reported in Discord by @evanjs: Deprecated lints in the docs don't expand:
https://rust-lang.github.io/rust-clippy/master/#misaligned_transmute
This is _probably_ because the doc comments need to be moved above the `pub LINT_NAME` line so that the lintlib.py script picks them up again.
| 1.0 | Lint docs: Deprecated lints don't expand - <!--
Hi there! Whether you've come to make a suggestion for a new lint, an improvement to an existing lint or to report a bug or a false positive in Clippy, you've come to the right place.
For bug reports and false positives, please include the output of `cargo clippy -V` in the report.
Thank you for using Clippy!
Write your comment below this line: -->
reported in Discord by @evanjs: Deprecated lints in the docs don't expand:
https://rust-lang.github.io/rust-clippy/master/#misaligned_transmute
This is _probably_ because the doc comments need to be moved above the `pub LINT_NAME` line so that the lintlib.py script picks them up again.
| non_priority | lint docs deprecated lints don t expand hi there whether you ve come to make a suggestion for a new lint an improvement to an existing lint or to report a bug or a false positive in clippy you ve come to the right place for bug reports and false positives please include the output of cargo clippy v in the report thank you for using clippy write your comment below this line reported in discord by evanjs deprecated lints in the docs don t expand this is probably because the doc comments need to be moved above the pub lint name line so that the lintlib py script picks them up again | 0 |
38,242 | 15,595,863,699 | IssuesEvent | 2021-03-18 15:17:54 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | closed | Document Repository | Implement refinements | Need: 2-Should Have Product: Moped Service: Dev Type: Enhancement | Initial implementation: https://github.com/cityofaustin/atd-moped/pull/230
### Files tab
- [x] Title should be "Files" to match tab
- [x] Remove "Project File Attachments" heading inside component
- [x] "File Description" ---> "Description"
- [x] "Created By" ---> "Uploaded by"
- [x] "Created Date" ---> "Date uploaded"
- [x] "File Size" ---> "File size"
- [x] File size should be rounded, no decimals
- [x] Common file size abbreviations; `KiB`, `MiB` ---> `KB`, `MB`

### Modal
- [x] "Upload Media" ---> "Upload a file"
- [x] Remove icons next to fields
- [x] "File Title" ---> "File name"
- [x] "File Description" ---> "Description"
- [x] "Save" ---> "Upload"

| 1.0 | Document Repository | Implement refinements - Initial implementation: https://github.com/cityofaustin/atd-moped/pull/230
### Files tab
- [x] Title should be "Files" to match tab
- [x] Remove "Project File Attachments" heading inside component
- [x] "File Description" ---> "Description"
- [x] "Created By" ---> "Uploaded by"
- [x] "Created Date" ---> "Date uploaded"
- [x] "File Size" ---> "File size"
- [x] File size should be rounded, no decimals
- [x] Common file size abbreviations; `KiB`, `MiB` ---> `KB`, `MB`

### Modal
- [x] "Upload Media" ---> "Upload a file"
- [x] Remove icons next to fields
- [x] "File Title" ---> "File name"
- [x] "File Description" ---> "Description"
- [x] "Save" ---> "Upload"

| non_priority | document repository implement refinements initial implementation files tab title should be files to match tab remove project file attachments heading inside component file description description created by uploaded by created date date uploaded file size file size file size should be rounded no decimals common file size abbreviations kib mib kb mb modal upload media upload a file remove icons next to fields file title file name file description description save upload | 0 |
281,198 | 24,370,761,352 | IssuesEvent | 2022-10-03 19:04:14 | neurobagel/annotation_tool | https://api.github.com/repos/neurobagel/annotation_tool | closed | Categorical annotations not in output if saved more than once | bug annotation page testing test case | Steps to reproduce:
- have a "categorical" column (e.g. Sex or Diagnosis)
- annotate the values
- hit "Save"
- make a change to any mapping
- hit "Save again"
- go to Download page
Expected behavior:
- Download page shows the last "saved" mappings
Actual behavior:
- Download page shows empty mappings for the column
**Tests**:
Not sure if these are better tested as component tests for the categorical annotation procedure or e2e of the entire annotation experience.
If I categorize a column as "Sex" (or "Diagnosis") and then completely annotate the values of that column:
- [x] then the store should not be updated (or component shouldn't emit an update event) if I haven't hit "save" yet
- [x] once I hit "save", the store should be updated (and/or component should emit update event with the correct data)
- [x] if I change the annotations after I have already made annotations and hit save a second time (more than once), then the store should reflect the newly updated annotations (or component emit update event with new data)
- [x] when I navigate to the download page after a 1+x annotation save workflow, the download page column should contain the mappings I have just created (i.e. the words should appear, order is irrelevant)

| 2.0 | Categorical annotations not in output if saved more than once - Steps to reproduce:
- have a "categorical" column (e.g. Sex or Diagnosis)
- annotate the values
- hit "Save"
- make a change to any mapping
- hit "Save again"
- go to Download page
Expected behavior:
- Download page shows the last "saved" mappings
Actual behavior:
- Download page shows empty mappings for the column
**Tests**:
Not sure if these are better tested as component tests for the categorical annotation procedure or e2e of the entire annotation experience.
If I categorize a column as "Sex" (or "Diagnosis") and then completely annotate the values of that column:
- [x] then the store should not be updated (or component shouldn't emit an update event) if I haven't hit "save" yet
- [x] once I hit "save", the store should be updated (and/or component should emit update event with the correct data)
- [x] if I change the annotations after I have already made annotations and hit save a second time (more than once), then the store should reflect the newly updated annotations (or component emit update event with new data)
- [x] when I navigate to the download page after a 1+x annotation save workflow, the download page column should contain the mappings I have just created (i.e. the words should appear, order is irrelevant)

| non_priority | categorical annotations not in output if saved more than once steps to reproduce have a categorical column e g sex or diagnosis annotate the values hit save make a change to any mapping hit save again go to download page expected behavior download page shows the last saved mappings actual behavior download page shows empty mappings for the column tests not sure if these are better tested as component tests for the categorical annotation procedure or of the entire annotation experience if i categorize a column as sex or diagnosis and then completely annotate the values of that column then the store should not be updated or component shouldn t emit an update event if i haven t hit save yet once i hit save the store should be updated and or component should emit update event with the correct data if i change the annotations after i have already made annotations and hit save a second time more than once then the store should reflect the newly updated annotations or component emit update event with new data when i navigate to the download page after a x annotation save workflow the download page column should contain the mappings i have just created i e the words should appear order is irrelevant | 0 |
351,366 | 31,998,570,037 | IssuesEvent | 2023-09-21 10:45:38 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | closed | Fix manipulations.test_jax_tile | JAX Frontend Sub Task Failing Test | | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/6260222171"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/6260222171"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/6260222171"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/6260222171"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/6260222171"><img src=https://img.shields.io/badge/-success-success></a>
| 1.0 | Fix manipulations.test_jax_tile - | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/6260222171"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/6260222171"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/6260222171"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/6260222171"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/6260222171"><img src=https://img.shields.io/badge/-success-success></a>
| non_priority | fix manipulations test jax tile numpy a href src jax a href src tensorflow a href src torch a href src paddle a href src | 0 |
2,915 | 2,651,586,917 | IssuesEvent | 2015-03-16 12:41:01 | 18F/myusa | https://api.github.com/repos/18F/myusa | opened | Landing page content & design revamp | 3-content 3-design p1 task | Goal: 1) address user testing feedback, 2) resolve content & hierarchy issues on landing page
[Landing page (version 1 with user testing notes, on Invision)](https://projects.invisionapp.com/d/main#/console/2318574/62062701/comments)
* @esgoodman & @kategarklavs did user testing on this version
* Feedback & content suggestions are within comments on Invision.

| 1.0 | Landing page content & design revamp - Goal: 1) address user testing feedback, 2) resolve content & hierarchy issues on landing page
[Landing page (version 1 with user testing notes, on Invision)](https://projects.invisionapp.com/d/main#/console/2318574/62062701/comments)
* @esgoodman & @kategarklavs did user testing on this version
* Feedback & content suggestions are within comments on Invision.

| non_priority | landing page content design revamp goal address user testing feedback resolve content hierarchy issues on landing page esgoodman kategarklavs did user testing on this version feedback content suggestions are within comments on invision | 0 |
83,742 | 10,429,629,453 | IssuesEvent | 2019-09-17 03:34:07 | samtecspg/articulate | https://api.github.com/repos/samtecspg/articulate | opened | Improve design of webhook page | needs design ui | Given a set of new changes on the webhooks we had the need to develop without having a proper design from @broham89.
This is currently the webhook page:

I think there is room for improvement here. | 1.0 | Improve design of webhook page - Given a set of new changes on the webhooks we had the need to develop without having a proper design from @broham89.
This is currently the webhook page:

I think there is room for improvement here. | non_priority | improve design of webhook page given a set of new changes on the webhooks we had the need to develop without having a proper design from this is currently the webhook page i think there is room for improvement here | 0 |
70,194 | 7,179,196,501 | IssuesEvent | 2018-01-31 18:52:54 | Microsoft/vscode | https://api.github.com/repos/Microsoft/vscode | closed | Test pattern-matching when clause | testplan-item | Test for: #26044
Complexity: 2
- [x] Any OS - @aeschli
- [x] Any OS - @rebornix
There is a new context key operator and it's regex-matching. The syntax is `name =~ /regex/` and it's supported when customising keybindings and when contributing menu items (from extensions). Test that
* you can use the new context key expression as desired, e.g try to contribute an explorer action for `f2{1,4}`-files
* you can use the new context key when configuring keybindings
* you cannot break it | 1.0 | Test pattern-matching when clause - Test for: #26044
Complexity: 2
- [x] Any OS - @aeschli
- [x] Any OS - @rebornix
There is a new context key operator and it's regex-matching. The syntax is `name =~ /regex/` and it's supported when customising keybindings and when contributing menu items (from extensions). Test that
* you can use the new context key expression as desired, e.g try to contribute an explorer action for `f2{1,4}`-files
* you can use the new context key when configuring keybindings
* you cannot break it | non_priority | test pattern matching when clause test for complexity any os aeschli any os rebornix there is a new context key operator and it s regex matching the syntax is name regex and it s supported when customising keybindings and when contributing menu items from extensions test that you can use the new context key expression as desired e g try to contribute an explorer action for files you can use the new context key when configuring keybindings you cannot break it | 0 |
426,326 | 29,515,841,556 | IssuesEvent | 2023-06-04 13:28:36 | scylladb/scylladb | https://api.github.com/repos/scylladb/scylladb | opened | Document repair-based tombstone removal | repair Documentation | I had in https://github.com/scylladb/scylladb/issues/14051 a discussion with a user that suspects they have too many tombstones and would have liked to get rid of them. I told them we have a new feature called "Repair-based tombstone GC" which can remove all the tombstone from his table without waiting for gc_grace_seconds. I found a blog post about it https://www.scylladb.com/2022/06/30/preventing-data-resurrection-with-repair-based-tombstone-garbage-collection/ and found it was added in Scylla 5.0 as experimental and GA since Scylla 5.2 - but wasn't able to find proper documentation for this feature. Do we have such a document?
A search in our documentation site found https://docs.scylladb.com/stable/kb/tombstones-flush.html but this document seems out of date - it asks you to manually manipulate gc_grace_second instead of using the new tombstone_gc configuration. It also mentions "large partition" for no reason (I think) - nothing it says is specifically about large partitions.
If we don't have a document about the new repair-based-gc we should write one. We should also link to it from relevant places (talking about gc_grace_second, etc.), and also remove old documents that suggest worse techniques to achieve this thing - like the above link.
CC @asias @annastuchlik | 1.0 | Document repair-based tombstone removal - I had in https://github.com/scylladb/scylladb/issues/14051 a discussion with a user that suspects they have too many tombstones and would have liked to get rid of them. I told them we have a new feature called "Repair-based tombstone GC" which can remove all the tombstone from his table without waiting for gc_grace_seconds. I found a blog post about it https://www.scylladb.com/2022/06/30/preventing-data-resurrection-with-repair-based-tombstone-garbage-collection/ and found it was added in Scylla 5.0 as experimental and GA since Scylla 5.2 - but wasn't able to find proper documentation for this feature. Do we have such a document?
A search in our documentation site found https://docs.scylladb.com/stable/kb/tombstones-flush.html but this document seems out of date - it asks you to manually manipulate gc_grace_second instead of using the new tombstone_gc configuration. It also mentions "large partition" for no reason (I think) - nothing it says is specifically about large partitions.
If we don't have a document about the new repair-based-gc we should write one. We should also link to it from relevant places (talking about gc_grace_second, etc.), and also remove old documents that suggest worse techniques to achieve this thing - like the above link.
CC @asias @annastuchlik | non_priority | document repair based tombstone removal i had in a discussion with a user that suspects they have too many tombstones and would have liked to get rid of them i told them we have a new feature called repair based tombstone gc which can remove all the tombstone from his table without waiting for gc grace seconds i found a blog post about it and found it was added in scylla as experimental and ga since scylla but wasn t able to find proper documentation for this feature do we have such a document a search in our documentation site found but this document seems out of date it asks you to manually manipulate gc grace second instead of using the new tombstone gc configuration it also mentions large partition for no reason i think nothing it says is specifically about large partitions if we don t have a document about the new repair based gc we should write one we should also link to it from relevant places talking about gc grace second etc and also remove old documents that suggest worse techniques to achieve this thing like the above link cc asias annastuchlik | 0 |
295,269 | 22,205,641,226 | IssuesEvent | 2022-06-07 14:40:41 | chef/chef-server | https://api.github.com/repos/chef/chef-server | closed | Update External Opensearch documentation with the user permissions required for Chef to work correctly with Opensearch. | Aspect: Documentation | Customers would like to leverage external Opensearch with their Chef Infra implementation. They currently have it working in a sandbox. However before going to production, they would like to know the minimum permissions required for the Opensearch user to have in order for Chef to work properly. They were not able to find this in documentation. | 1.0 | Update External Opensearch documentation with the user permissions required for Chef to work correctly with Opensearch. - Customers would like to leverage external Opensearch with their Chef Infra implementation. They currently have it working in a sandbox. However before going to production, they would like to know the minimum permissions required for the Opensearch user to have in order for Chef to work properly. They were not able to find this in documentation. | non_priority | update external opensearch documentation with the user permissions required for chef to work correctly with opensearch customers would like to leverage external opensearch with their chef infra implementation they currently have it working in a sandbox however before going to production they would like to know the minimum permissions required for the opensearch user to have in order for chef to work properly they were not able to find this in documentation | 0 |
451,647 | 32,037,499,406 | IssuesEvent | 2023-09-22 16:27:02 | ansible-middleware/amq | https://api.github.com/repos/ansible-middleware/amq | opened | Write the http://ansiblemiddleware.com/amq/main/masked_passwords.html | documentation good first issue hacktoberfest | ##### SUMMARY
<!--- Explain the problem briefly -->
The guide [Using custom encypted passwords](http://ansiblemiddleware.com/amq/main/masked_passwords.html) needs a tester and technical writer. Experiment and analyze the molecule test [here](https://github.com/ansible-middleware/amq/tree/main/molecule/mask_passwords), and using it write down the guide in markdown [here]( https://github.com/ansible-middleware/amq/blob/main/docs/masked_passwords.md).
##### ISSUE TYPE
- Documentation
| 1.0 | Write the http://ansiblemiddleware.com/amq/main/masked_passwords.html - ##### SUMMARY
<!--- Explain the problem briefly -->
The guide [Using custom encypted passwords](http://ansiblemiddleware.com/amq/main/masked_passwords.html) needs a tester and technical writer. Experiment and analyze the molecule test [here](https://github.com/ansible-middleware/amq/tree/main/molecule/mask_passwords), and using it write down the guide in markdown [here]( https://github.com/ansible-middleware/amq/blob/main/docs/masked_passwords.md).
##### ISSUE TYPE
- Documentation
| non_priority | write the summary the guide needs a tester and technical writer experiment and analyze the molecule test and using it write down the guide in markdown issue type documentation | 0 |
194,998 | 22,281,626,052 | IssuesEvent | 2022-06-11 01:16:46 | pustovitDmytro/node-package-tester | https://api.github.com/repos/pustovitDmytro/node-package-tester | opened | CVE-2022-31051 (Medium) detected in semantic-release-19.0.2.tgz | security vulnerability | ## CVE-2022-31051 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>semantic-release-19.0.2.tgz</b></p></summary>
<p>Automated semver compliant package publishing</p>
<p>Library home page: <a href="https://registry.npmjs.org/semantic-release/-/semantic-release-19.0.2.tgz">https://registry.npmjs.org/semantic-release/-/semantic-release-19.0.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/semantic-release/package.json</p>
<p>
Dependency Hierarchy:
- :x: **semantic-release-19.0.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/pustovitDmytro/node-package-tester/commit/e9f92222fae5f192fc141e650dbd0468173de3f5">e9f92222fae5f192fc141e650dbd0468173de3f5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
semantic-release is an open source npm package for automated version management and package publishing. In affected versions secrets that would normally be masked by semantic-release can be accidentally disclosed if they contain characters that are excluded from uri encoding by `encodeURI`. Occurrence is further limited to execution contexts where push access to the related repository is not available without modifying the repository url to inject credentials. Users are advised to upgrade. Users unable to upgrade should ensure that secrets that do not contain characters that are excluded from encoding with `encodeURI` when included in a URL are already masked properly.
<p>Publish Date: 2022-06-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-31051>CVE-2022-31051</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/semantic-release/semantic-release/security/advisories/GHSA-x2pg-mjhr-2m5x">https://github.com/semantic-release/semantic-release/security/advisories/GHSA-x2pg-mjhr-2m5x</a></p>
<p>Release Date: 2022-06-09</p>
<p>Fix Resolution: 19.0.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-31051 (Medium) detected in semantic-release-19.0.2.tgz - ## CVE-2022-31051 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>semantic-release-19.0.2.tgz</b></p></summary>
<p>Automated semver compliant package publishing</p>
<p>Library home page: <a href="https://registry.npmjs.org/semantic-release/-/semantic-release-19.0.2.tgz">https://registry.npmjs.org/semantic-release/-/semantic-release-19.0.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/semantic-release/package.json</p>
<p>
Dependency Hierarchy:
- :x: **semantic-release-19.0.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/pustovitDmytro/node-package-tester/commit/e9f92222fae5f192fc141e650dbd0468173de3f5">e9f92222fae5f192fc141e650dbd0468173de3f5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
semantic-release is an open source npm package for automated version management and package publishing. In affected versions secrets that would normally be masked by semantic-release can be accidentally disclosed if they contain characters that are excluded from uri encoding by `encodeURI`. Occurrence is further limited to execution contexts where push access to the related repository is not available without modifying the repository url to inject credentials. Users are advised to upgrade. Users unable to upgrade should ensure that secrets that do not contain characters that are excluded from encoding with `encodeURI` when included in a URL are already masked properly.
<p>Publish Date: 2022-06-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-31051>CVE-2022-31051</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/semantic-release/semantic-release/security/advisories/GHSA-x2pg-mjhr-2m5x">https://github.com/semantic-release/semantic-release/security/advisories/GHSA-x2pg-mjhr-2m5x</a></p>
<p>Release Date: 2022-06-09</p>
<p>Fix Resolution: 19.0.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in semantic release tgz cve medium severity vulnerability vulnerable library semantic release tgz automated semver compliant package publishing library home page a href path to dependency file package json path to vulnerable library node modules semantic release package json dependency hierarchy x semantic release tgz vulnerable library found in head commit a href found in base branch master vulnerability details semantic release is an open source npm package for automated version management and package publishing in affected versions secrets that would normally be masked by semantic release can be accidentally disclosed if they contain characters that are excluded from uri encoding by encodeuri occurrence is further limited to execution contexts where push access to the related repository is not available without modifying the repository url to inject credentials users are advised to upgrade users unable to upgrade should ensure that secrets that do not contain characters that are excluded from encoding with encodeuri when included in a url are already masked properly publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
239,931 | 26,244,233,789 | IssuesEvent | 2023-01-05 14:03:59 | MatBenfield/news | https://api.github.com/repos/MatBenfield/news | closed | [SecurityWeek] Wabtec Says Personal Information Compromised in Ransomware Attack | SecurityWeek Stale |
**Rail systems and locomotive manufacturer Wabtec has started sending notification letters to individuals whose personal information was stolen in a ransomware attack last year.**
The US-based firm provides railway equipment, systems, and services worldwide and has offices in the Americas, Australia, and Europe. The company has roughly 27,000 employees.
[read more](https://www.securityweek.com/wabtec-says-personal-information-compromised-ransomware-attack)
<https://www.securityweek.com/wabtec-says-personal-information-compromised-ransomware-attack>
| True | [SecurityWeek] Wabtec Says Personal Information Compromised in Ransomware Attack -
**Rail systems and locomotive manufacturer Wabtec has started sending notification letters to individuals whose personal information was stolen in a ransomware attack last year.**
The US-based firm provides railway equipment, systems, and services worldwide and has offices in the Americas, Australia, and Europe. The company has roughly 27,000 employees.
[read more](https://www.securityweek.com/wabtec-says-personal-information-compromised-ransomware-attack)
<https://www.securityweek.com/wabtec-says-personal-information-compromised-ransomware-attack>
| non_priority | wabtec says personal information compromised in ransomware attack rail systems and locomotive manufacturer wabtec has started sending notification letters to individuals whose personal information was stolen in a ransomware attack last year the us based firm provides railway equipment systems and services worldwide and has offices in the americas australia and europe the company has roughly employees | 0 |
267,520 | 28,509,076,995 | IssuesEvent | 2023-04-19 01:33:20 | dpteam/RK3188_TABLET | https://api.github.com/repos/dpteam/RK3188_TABLET | closed | CVE-2022-41222 (High) detected in linuxv3.0.70 - autoclosed | Mend: dependency security vulnerability | ## CVE-2022-41222 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv3.0.70</b></p></summary>
<p>
<p>Development tree</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/keithp/linux.git>https://git.kernel.org/pub/scm/linux/kernel/git/keithp/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/mremap.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/mremap.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/mremap.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
mm/mremap.c in the Linux kernel before 5.13.3 has a use-after-free via a stale TLB because an rmap lock is not held during a PUD move.
<p>Publish Date: 2022-09-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41222>CVE-2022-41222</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2022-41222">https://www.linuxkernelcves.com/cves/CVE-2022-41222</a></p>
<p>Release Date: 2022-09-21</p>
<p>Fix Resolution: v5.4.211,v5.10.137,v5.12.18,v5.13.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-41222 (High) detected in linuxv3.0.70 - autoclosed - ## CVE-2022-41222 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv3.0.70</b></p></summary>
<p>
<p>Development tree</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/keithp/linux.git>https://git.kernel.org/pub/scm/linux/kernel/git/keithp/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/mremap.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/mremap.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/mremap.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
mm/mremap.c in the Linux kernel before 5.13.3 has a use-after-free via a stale TLB because an rmap lock is not held during a PUD move.
<p>Publish Date: 2022-09-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41222>CVE-2022-41222</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2022-41222">https://www.linuxkernelcves.com/cves/CVE-2022-41222</a></p>
<p>Release Date: 2022-09-21</p>
<p>Fix Resolution: v5.4.211,v5.10.137,v5.12.18,v5.13.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in autoclosed cve high severity vulnerability vulnerable library development tree library home page a href found in head commit a href found in base branch master vulnerable source files mm mremap c mm mremap c mm mremap c vulnerability details mm mremap c in the linux kernel before has a use after free via a stale tlb because an rmap lock is not held during a pud move publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
193,566 | 22,216,199,846 | IssuesEvent | 2022-06-08 02:05:59 | maddyCode23/linux-4.1.15 | https://api.github.com/repos/maddyCode23/linux-4.1.15 | reopened | CVE-2021-42008 (High) detected in linux-stable-rtv4.1.33 | security vulnerability | ## CVE-2021-42008 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/maddyCode23/linux-4.1.15/commit/f1f3d2b150be669390b32dfea28e773471bdd6e7">f1f3d2b150be669390b32dfea28e773471bdd6e7</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/hamradio/6pack.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/hamradio/6pack.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The decode_data function in drivers/net/hamradio/6pack.c in the Linux kernel before 5.13.13 has a slab out-of-bounds write. Input from a process that has the CAP_NET_ADMIN capability can lead to root access.
<p>Publish Date: 2021-10-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-42008>CVE-2021-42008</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2021-42008">https://www.linuxkernelcves.com/cves/CVE-2021-42008</a></p>
<p>Release Date: 2021-10-05</p>
<p>Fix Resolution: v4.4.282,v4.9.281,v4.14.245,v4.19.205,v5.4.143,v5.10.61,v5.13.13,v5.14-rc7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-42008 (High) detected in linux-stable-rtv4.1.33 - ## CVE-2021-42008 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/maddyCode23/linux-4.1.15/commit/f1f3d2b150be669390b32dfea28e773471bdd6e7">f1f3d2b150be669390b32dfea28e773471bdd6e7</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/hamradio/6pack.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/hamradio/6pack.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The decode_data function in drivers/net/hamradio/6pack.c in the Linux kernel before 5.13.13 has a slab out-of-bounds write. Input from a process that has the CAP_NET_ADMIN capability can lead to root access.
<p>Publish Date: 2021-10-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-42008>CVE-2021-42008</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2021-42008">https://www.linuxkernelcves.com/cves/CVE-2021-42008</a></p>
<p>Release Date: 2021-10-05</p>
<p>Fix Resolution: v4.4.282,v4.9.281,v4.14.245,v4.19.205,v5.4.143,v5.10.61,v5.13.13,v5.14-rc7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linux stable cve high severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files drivers net hamradio c drivers net hamradio c vulnerability details the decode data function in drivers net hamradio c in the linux kernel before has a slab out of bounds write input from a process that has the cap net admin capability can lead to root access publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
141,401 | 18,984,067,190 | IssuesEvent | 2021-11-21 12:12:16 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | closed | Vulnerability roundup 93: bsdiff-4.3: 1 advisory [9.8] | 1.severity: security | [search](https://search.nix.gsc.io/?q=bsdiff&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=bsdiff+in%3Apath&type=Code)
* [ ] [CVE-2020-14315](https://nvd.nist.gov/vuln/detail/CVE-2020-14315) CVSSv3=9.8 (nixos-20.03, nixos-20.09, nixos-unstable)
Scanned versions: nixos-20.03: 0d0660fde3b; nixos-20.09: ad3a5d5092e; nixos-unstable: 84d74ae9c9c.
Cc @thoughtpolice
| True | Vulnerability roundup 93: bsdiff-4.3: 1 advisory [9.8] - [search](https://search.nix.gsc.io/?q=bsdiff&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=bsdiff+in%3Apath&type=Code)
* [ ] [CVE-2020-14315](https://nvd.nist.gov/vuln/detail/CVE-2020-14315) CVSSv3=9.8 (nixos-20.03, nixos-20.09, nixos-unstable)
Scanned versions: nixos-20.03: 0d0660fde3b; nixos-20.09: ad3a5d5092e; nixos-unstable: 84d74ae9c9c.
Cc @thoughtpolice
| non_priority | vulnerability roundup bsdiff advisory nixos nixos nixos unstable scanned versions nixos nixos nixos unstable cc thoughtpolice | 0 |
176,623 | 14,592,648,106 | IssuesEvent | 2020-12-19 18:37:17 | saltstack/salt | https://api.github.com/repos/saltstack/salt | opened | [DOCS] Default value for auth_timeout | Documentation | **Description**
[Web documentation](https://docs.saltstack.com/en/latest/ref/configuration/minion.html#auth-timeout) and the [var/conf/minion file](https://github.com/markuskramerIgitt/salt/blob/214ae8a9af972b9c5f50bf13f9f0b76d092af952/conf/minion#L245) state that Minions have a `auth_timeout` default of **60 seconds**.
This value was 3 or 5 and hard-coded for a while.
Thanks to [a PR in 2016](https://github.com/saltstack/salt/commit/998c3db8bf983c693f9602b01e8bddf7cbfba913) by @skizunov, Minions have a `auth_timeout` default of [5 seconds](https://github.com/markuskramerIgitt/salt/blob/214ae8a9af972b9c5f50bf13f9f0b76d092af952/salt/config/__init__.py#L1206).
**Suggested Fix**
Correct to **5 seconds** in both places
**Additional context**
For high latency networks, `auth_timeout` needs to be increased (e.g. issue #11806)
| 1.0 | [DOCS] Default value for auth_timeout - **Description**
[Web documentation](https://docs.saltstack.com/en/latest/ref/configuration/minion.html#auth-timeout) and the [var/conf/minion file](https://github.com/markuskramerIgitt/salt/blob/214ae8a9af972b9c5f50bf13f9f0b76d092af952/conf/minion#L245) state that Minions have a `auth_timeout` default of **60 seconds**.
This value was 3 or 5 and hard-coded for a while.
Thanks to [a PR in 2016](https://github.com/saltstack/salt/commit/998c3db8bf983c693f9602b01e8bddf7cbfba913) by @skizunov, Minions have a `auth_timeout` default of [5 seconds](https://github.com/markuskramerIgitt/salt/blob/214ae8a9af972b9c5f50bf13f9f0b76d092af952/salt/config/__init__.py#L1206).
**Suggested Fix**
Correct to **5 seconds** in both places
**Additional context**
For high latency networks, `auth_timeout` needs to be increased (e.g. issue #11806)
| non_priority | default value for auth timeout description and the state that minions have a auth timeout default of seconds this value was or and hard coded for a while thanks to by skizunov minions have a auth timeout default of suggested fix correct to seconds in both places additional context for high latency networks auth timeout needs to be increased e g issue | 0 |
7,000 | 7,834,314,936 | IssuesEvent | 2018-06-16 12:11:35 | Automattic/wp-calypso | https://api.github.com/repos/Automattic/wp-calypso | closed | Store: WCS-powered USPS and Canada Post shipping methods | Epic Store Store Services [Type] Task | Umbrella issue for all the work related to porting the USPS and Canada Post shipping methods for live rates into Calypso.
Also part of this epic, these issues from `woocommerce-services`:
- https://github.com/Automattic/woocommerce-services/issues/1212
- https://github.com/Automattic/woocommerce-services/issues/1213 (Optional)
- https://github.com/Automattic/woocommerce-services/issues/1214 (Optional)
- https://github.com/Automattic/woocommerce-services/issues/1215 (Optional)
- https://github.com/Automattic/woocommerce-services/issues/938
cc/ @jeffstieler @justinshreve @marcinbot Please tell me if you think I've overlooked something. | 1.0 | Store: WCS-powered USPS and Canada Post shipping methods - Umbrella issue for all the work related to porting the USPS and Canada Post shipping methods for live rates into Calypso.
Also part of this epic, these issues from `woocommerce-services`:
- https://github.com/Automattic/woocommerce-services/issues/1212
- https://github.com/Automattic/woocommerce-services/issues/1213 (Optional)
- https://github.com/Automattic/woocommerce-services/issues/1214 (Optional)
- https://github.com/Automattic/woocommerce-services/issues/1215 (Optional)
- https://github.com/Automattic/woocommerce-services/issues/938
cc/ @jeffstieler @justinshreve @marcinbot Please tell me if you think I've overlooked something. | non_priority | store wcs powered usps and canada post shipping methods umbrella issue for all the work related to porting the usps and canada post shipping methods for live rates into calypso also part of this epic these issues from woocommerce services optional optional optional cc jeffstieler justinshreve marcinbot please tell me if you think i ve overlooked something | 0 |
35,321 | 9,561,925,339 | IssuesEvent | 2019-05-04 03:33:31 | openshiftio/openshift.io | https://api.github.com/repos/openshiftio/openshift.io | closed | Osio Pipeline: Override BuildConfig timeout | team/build-cd type/user-story | We need to find a way to override the BuildConfig timeout.
Patching the spec of the buildconfig with the [completionDeadlineSeconds](https://docs.openshift.com/container-platform/3.6/dev_guide/builds/advanced_build_operations.html#builds-setting-maximum-duration) option,
Ideally we want to have a different timeout by "cluster", i.e: if it's on OSIO
or on OSD.
Osio Pipeline issue: https://github.com/fabric8io/osio-pipeline/issues/93 | 1.0 | Osio Pipeline: Override BuildConfig timeout - We need to find a way to override the BuildConfig timeout.
Patching the spec of the buildconfig with the [completionDeadlineSeconds](https://docs.openshift.com/container-platform/3.6/dev_guide/builds/advanced_build_operations.html#builds-setting-maximum-duration) option,
Ideally we want to have a different timeout by "cluster", i.e: if it's on OSIO
or on OSD.
Osio Pipeline issue: https://github.com/fabric8io/osio-pipeline/issues/93 | non_priority | osio pipeline override buildconfig timeout we need to find a way to override the buildconfig timeout patching the spec of the buildconfig with the option ideally we want to have a different timeout by cluster i e if it s on osio or on osd osio pipeline issue | 0 |
62,381 | 7,574,721,864 | IssuesEvent | 2018-04-23 21:58:31 | doug-m/CollectorAuroraTesting | https://api.github.com/repos/doug-m/CollectorAuroraTesting | closed | Clarification on expected behavior when removing a map that was downloaded | A-design feedback C-by design | ### Issue
In previous versions of Collector, when removing a map that had been downloaded for offline use, the user had the option of whether they wanted to remove just the data, or the basemap and the data. Is this still possible? When removing the map it didn't present me with any options. This may be expected in Aurora but may be confusing for previous Collector users.
### Expected Behavior
### Map and Credentials
### Steps to Reproduce
1) Download the map for offline use
2) Remove the map-- user isn't provided with options about what they would like to remove
### Device Information
* Device: iPhone 6+
* OS Version: 11.x
<!---Attach crash log or screenshots-->
| 2.0 | Clarification on expected behavior when removing a map that was downloaded - ### Issue
In previous versions of Collector, when removing a map that had been downloaded for offline use, the user had the option of whether they wanted to remove just the data, or the basemap and the data. Is this still possible? When removing the map it didn't present me with any options. This may be expected in Aurora but may be confusing for previous Collector users.
### Expected Behavior
### Map and Credentials
### Steps to Reproduce
1) Download the map for offline use
2) Remove the map-- user isn't provided with options about what they would like to remove
### Device Information
* Device: iPhone 6+
* OS Version: 11.x
<!---Attach crash log or screenshots-->
| non_priority | clarification on expected behavior when removing a map that was downloaded issue in previous versions of collector when removing a map that had been downloaded for offline use the user had the option of whether they wanted to remove just the data or the basemap and the data is this still possible when removing the map it didn t present me with any options this may be expected in aurora but may be confusing for previous collector users expected behavior map and credentials steps to reproduce download the map for offline use remove the map user isn t provided with options about what they would like to remove device information device iphone os version x | 0 |
118,475 | 11,980,911,019 | IssuesEvent | 2020-04-07 10:09:00 | AY1920S2-CS2103T-W17-4/main | https://api.github.com/repos/AY1920S2-CS2103T-W17-4/main | closed | [PE-D] Statistics format error | type.DocumentationBug type.FunctionalityBug | No labels for pie chart and table cannot be seen, also the student table cannot display for more than 5 students.

Maybe it is because it is still in working process given that it is not included in UG, so the severity is set to be very low.
-------------
Labels: `severity.VeryLow` `type.FunctionalityBug`
original: ZhangYiping126/ped#9 | 1.0 | [PE-D] Statistics format error - No labels for pie chart and table cannot be seen, also the student table cannot display for more than 5 students.

Maybe it is because it is still in working process given that it is not included in UG, so the severity is set to be very low.
-------------
Labels: `severity.VeryLow` `type.FunctionalityBug`
original: ZhangYiping126/ped#9 | non_priority | statistics format error no labels for pie chart and table cannot be seen also the student table cannot display for more than students maybe it is because it is still in working process given that it is not included in ug so the severity is set to be very low labels severity verylow type functionalitybug original ped | 0 |
10,196 | 7,935,547,838 | IssuesEvent | 2018-07-09 05:56:29 | gluster/glusterd2 | https://api.github.com/repos/gluster/glusterd2 | opened | Add support for glusterfs client authorization | FW: Security FW: Volume Management GCS-Blocker | GlusterFS supports many methods to allow or disallow certain clients to access volume. Users can specify patterns of host/IP addresses using options such as `auth.allow` | True | Add support for glusterfs client authorization - GlusterFS supports many methods to allow or disallow certain clients to access volume. Users can specify patterns of host/IP addresses using options such as `auth.allow` | non_priority | add support for glusterfs client authorization glusterfs supports many methods to allow or disallow certain clients to access volume users can specify patterns of host ip addresses using options such as auth allow | 0 |
119,888 | 12,053,773,633 | IssuesEvent | 2020-04-15 09:57:02 | unoplatform/uno | https://api.github.com/repos/unoplatform/uno | opened | does support scan QRCode ? | kind/contributor-experience kind/documentation triage/untriaged | <!-- Please only use this template for submitting enhancement requests -->
## What would you like to be added:
I can use CameraCaptureUI to capture picture now, but I must click the system taking picture button to take a picture, can I skip this step, just get the picture by code when we need to scan a qrcode?
#### my test code:
```C#
var captureUI = new CameraCaptureUI();
captureUI.PhotoSettings.Format = CameraCaptureUIPhotoFormat.Jpeg;
captureUI.PhotoSettings.CroppedSizeInPixels = new Size(200, 200);
var photo = await captureUI.CaptureFileAsync(CameraCaptureUIMode.PhotoOrVideo);
```
## Why is this needed:
## For which Platform:
- [x] iOS
- [x] Android
- [ ] WebAssembly
- [ ] WebAssembly renderers for Xamarin.Forms
- [ ] macOS
- [x] Windows
## Anything else we need to know?
<!-- We would love to know of any friction, apart from knowledge, that prevented you from sending in a pull-request -->
| 1.0 | does support scan QRCode ? - <!-- Please only use this template for submitting enhancement requests -->
## What would you like to be added:
I can use CameraCaptureUI to capture picture now, but I must click the system taking picture button to take a picture, can I skip this step, just get the picture by code when we need to scan a qrcode?
#### my test code:
```C#
var captureUI = new CameraCaptureUI();
captureUI.PhotoSettings.Format = CameraCaptureUIPhotoFormat.Jpeg;
captureUI.PhotoSettings.CroppedSizeInPixels = new Size(200, 200);
var photo = await captureUI.CaptureFileAsync(CameraCaptureUIMode.PhotoOrVideo);
```
## Why is this needed:
## For which Platform:
- [x] iOS
- [x] Android
- [ ] WebAssembly
- [ ] WebAssembly renderers for Xamarin.Forms
- [ ] macOS
- [x] Windows
## Anything else we need to know?
<!-- We would love to know of any friction, apart from knowledge, that prevented you from sending in a pull-request -->
| non_priority | does support scan qrcode what would you like to be added i can use cameracaptureui to capture picture now but i must click the system taking picture button to take a picture can i skip this step just get the picture by code when we need to scan a qrcode my test code c var captureui new cameracaptureui captureui photosettings format cameracaptureuiphotoformat jpeg captureui photosettings croppedsizeinpixels new size var photo await captureui capturefileasync cameracaptureuimode photoorvideo why is this needed for which platform ios android webassembly webassembly renderers for xamarin forms macos windows anything else we need to know | 0 |
27,080 | 5,312,820,129 | IssuesEvent | 2017-02-13 10:15:01 | ptools/ptools | https://api.github.com/repos/ptools/ptools | opened | Write a developer's guide | documentation | Developer's guide should include:
- what are the repositories
- explanations on PTools branching model
- detail branch permissions
- merge policy (unit tests, etc.)
| 1.0 | Write a developer's guide - Developer's guide should include:
- what are the repositories
- explanations on PTools branching model
- detail branch permissions
- merge policy (unit tests, etc.)
| non_priority | write a developer s guide developer s guide should include what are the repositories explanations on ptools branching model detail branch permissions merge policy unit tests etc | 0 |
15,721 | 9,600,990,531 | IssuesEvent | 2019-05-10 10:50:42 | jinuem/Cordova-Examples | https://api.github.com/repos/jinuem/Cordova-Examples | opened | CVE-2019-6286 (Medium) detected in node-sass-v4.11.0 | security vulnerability | ## CVE-2019-6286 - Medium Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.11.0</b></p></summary>
<p>
<p>:rainbow: Node.js bindings to libsass</p>
<p>Library home page: <a href=https://github.com/sass/node-sass.git>https://github.com/sass/node-sass.git</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Library Source Files (128)</summary>
<p></p>
<p> * The source files were matched to this source library based on a best effort match. Source libraries are selected from a list of probable public libraries.</p>
<p>
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/libsass/src/to_value.hpp
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/libsass/src/source_map.cpp
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/src/constants.hpp
- /Cordova-Examples/ionic_openwhisk/node_modules/node-sass/src/libsass/src/to_c.hpp
- /Cordova-Examples/ionicWeatherV2/node_modules/node-sass/src/libsass/src/node.hpp
- /Cordova-Examples/fixcontacts/node_modules/node-sass/src/libsass/src/memory_manager.hpp
- /Cordova-Examples/db2/node_modules/node-sass/src/libsass/src/expand.cpp
- /Cordova-Examples/ionicauth2/node_modules/node-sass/src/libsass/src/listize.cpp
- /Cordova-Examples/fixcontacts/node_modules/node-sass/src/libsass/src/output.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/lib/extensions.js
- /Cordova-Examples/ionicauth2/node_modules/node-sass/src/libsass/src/parser.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/backtrace.hpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/units.hpp
- /Cordova-Examples/ionicWeatherV2/node_modules/node-sass/src/libsass/test/test_node.cpp
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/sass_types/number.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/scripts/build.js
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/custom_importer_bridge.cpp
- /Cordova-Examples/ionicAuth2Social/node_modules/node-sass/src/libsass/src/sass_util.hpp
- /Cordova-Examples/db1/node_modules/node-sass/src/sass_types/sass_value_wrapper.h
- /Cordova-Examples/db2/node_modules/node-sass/src/sass_types/string.cpp
- /Cordova-Examples/db1/node_modules/node-sass/src/sass_types/null.cpp
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/contrib/plugin.cpp
- /Cordova-Examples/ionicWeatherV2/node_modules/node-sass/src/libsass/src/listize.hpp
- /Cordova-Examples/ionicAuth2Social/node_modules/node-sass/src/libsass/src/lexer.hpp
- /Cordova-Examples/sidemenudemo/node_modules/node-sass/src/libsass/src/sass_util.cpp
- /Cordova-Examples/db2/node_modules/node-sass/src/libsass/test/test_superselector.cpp
- /Cordova-Examples/fixcontacts/node_modules/node-sass/src/libsass/src/units.cpp
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/src/cencode.c
- /Cordova-Examples/db3/node_modules/node-sass/src/libsass/src/ast_factory.hpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/sass_functions.cpp
- /Cordova-Examples/ionicauth2/node_modules/node-sass/src/libsass/src/ast.hpp
- /Cordova-Examples/sidemenudemo/node_modules/node-sass/src/libsass/src/remove_placeholders.hpp
- /Cordova-Examples/db2/node_modules/node-sass/src/libsass/src/utf8_string.hpp
- /Cordova-Examples/db3/node_modules/node-sass/src/libsass/src/memory_manager.cpp
- /Cordova-Examples/ionic_openwhisk/node_modules/node-sass/src/libsass/src/sass_values.cpp
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/callback_bridge.h
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/test/cli.js
- /Cordova-Examples/ionicWeatherV2/node_modules/node-sass/src/libsass/src/constants.cpp
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/libsass/src/to_c.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/test/lowlevel.js
- /Cordova-Examples/sidemenudemo/node_modules/node-sass/src/libsass/src/remove_placeholders.cpp
- /Cordova-Examples/db3/node_modules/node-sass/src/sass_types/color.cpp
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/libsass/src/util.cpp
- /Cordova-Examples/ionicWeatherV2/node_modules/node-sass/src/libsass/src/eval.cpp
- /Cordova-Examples/ionicAuth2Social/node_modules/node-sass/src/libsass/src/sass_context.hpp
- /Cordova-Examples/ionic_openwhisk/node_modules/node-sass/src/libsass/src/output.hpp
- /Cordova-Examples/sidemenudemo/node_modules/node-sass/src/libsass/src/operation.hpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/lib/render.js
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/custom_function_bridge.cpp
- /Cordova-Examples/db1/node_modules/node-sass/src/libsass/src/inspect.hpp
- /Cordova-Examples/ionicauth2/node_modules/node-sass/src/libsass/src/sass.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/test/errors.js
- /Cordova-Examples/ionic_openwhisk/node_modules/node-sass/src/libsass/src/file.hpp
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/libsass/include/sass/values.h
- /Cordova-Examples/db1/node_modules/node-sass/src/libsass/src/paths.hpp
- /Cordova-Examples/ionic_openwhisk/node_modules/node-sass/src/libsass/src/sass_values.hpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/lib/errors.js
- /Cordova-Examples/ionic_openwhisk/node_modules/node-sass/src/sass_types/boolean.h
- /Cordova-Examples/sidemenudemo/node_modules/node-sass/src/libsass/src/error_handling.hpp
- /Cordova-Examples/fixcontacts/node_modules/node-sass/src/libsass/test/test_unification.cpp
- /Cordova-Examples/sidemenudemo/node_modules/node-sass/src/libsass/src/sass.hpp
- /Cordova-Examples/ionicAuth2Social/node_modules/node-sass/src/sass_types/list.h
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/file.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/scripts/coverage.js
- /Cordova-Examples/ionicAuth2Social/node_modules/node-sass/src/libsass/src/position.cpp
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/src/expand.hpp
- /Cordova-Examples/ionicWeatherV2/node_modules/node-sass/src/libsass/src/context.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/prelexer.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/inspect.cpp
- /Cordova-Examples/db3/node_modules/node-sass/src/libsass/src/extend.cpp
- /Cordova-Examples/ionic_openwhisk/node_modules/node-sass/src/libsass/src/parser.hpp
- /Cordova-Examples/ionicWeatherV2/node_modules/node-sass/src/sass_types/list.cpp
- /Cordova-Examples/db3/node_modules/node-sass/src/libsass/src/bind.cpp
- /Cordova-Examples/fixcontacts/node_modules/node-sass/src/sass_types/map.cpp
- /Cordova-Examples/ionic_openwhisk/node_modules/node-sass/src/libsass/src/sass_context.cpp
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/src/values.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/test/api.js
- /Cordova-Examples/ionicWeatherV2/node_modules/node-sass/src/libsass/src/emitter.cpp
- /Cordova-Examples/ionicauth2/node_modules/node-sass/src/libsass/src/debugger.hpp
- /Cordova-Examples/fixcontacts/node_modules/node-sass/src/libsass/src/ast_fwd_decl.hpp
- /Cordova-Examples/ionic_openwhisk/node_modules/node-sass/src/libsass/src/util.hpp
- /Cordova-Examples/db3/node_modules/node-sass/src/libsass/src/cssize.cpp
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/sass_context_wrapper.cpp
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/src/error_handling.cpp
- /Cordova-Examples/ionicauth2/node_modules/node-sass/src/libsass/src/position.hpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/test/spec.js
- /Cordova-Examples/ionicauth2/node_modules/node-sass/src/libsass/src/ast_def_macros.hpp
- /Cordova-Examples/fixcontacts/node_modules/node-sass/src/libsass/src/emitter.hpp
- /Cordova-Examples/fixcontacts/node_modules/node-sass/src/libsass/src/eval.hpp
- /Cordova-Examples/db1/node_modules/node-sass/src/libsass/src/sass2scss.cpp
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/src/functions.cpp
- /Cordova-Examples/db1/node_modules/node-sass/src/libsass/src/functions.hpp
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/libsass/src/prelexer.hpp
- /Cordova-Examples/ionicauth2/node_modules/node-sass/src/sass_types/boolean.cpp
- /Cordova-Examples/ionicWeatherV2/node_modules/node-sass/src/custom_importer_bridge.h
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/libsass/src/ast.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/utf8_string.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/include/sass/functions.h
- /Cordova-Examples/fixcontacts/node_modules/node-sass/src/libsass/src/lexer.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/test/runtime.js
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/scripts/install.js
- /Cordova-Examples/db3/node_modules/node-sass/src/sass_context_wrapper.h
- /Cordova-Examples/sidemenudemo/node_modules/node-sass/src/libsass/src/b64/encode.h
- /Cordova-Examples/db2/node_modules/node-sass/src/libsass/src/base64vlq.cpp
- /Cordova-Examples/ionic_openwhisk/node_modules/node-sass/src/libsass/src/to_value.cpp
- /Cordova-Examples/db2/node_modules/node-sass/src/libsass/src/cssize.hpp
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/src/environment.cpp
- /Cordova-Examples/sidemenudemo/node_modules/node-sass/src/libsass/src/c99func.c
- /Cordova-Examples/fixcontacts/node_modules/node-sass/src/libsass/test/test_subset_map.cpp
- /Cordova-Examples/sidemenudemo/node_modules/node-sass/src/libsass/src/subset_map.hpp
- /Cordova-Examples/db3/node_modules/node-sass/src/libsass/include/sass/base.h
- /Cordova-Examples/ionicWeatherV2/node_modules/node-sass/src/binding.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/source_map.hpp
- /Cordova-Examples/db1/node_modules/node-sass/src/libsass/include/sass2scss.h
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/libsass/src/plugins.cpp
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/src/extend.hpp
- /Cordova-Examples/sidemenudemo/node_modules/node-sass/src/libsass/src/node.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/plugins.hpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/lib/index.js
- /Cordova-Examples/ionicAuth2Social/node_modules/node-sass/src/libsass/src/environment.hpp
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/libsass/include/sass/context.h
- /Cordova-Examples/ionicAuth2Social/node_modules/node-sass/src/sass_types/color.h
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/src/color_maps.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/json.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/debug.hpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/context.hpp
- /Cordova-Examples/ionicauth2/node_modules/node-sass/src/sass_types/factory.cpp
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/src/color_maps.hpp
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass 3.5.5, a heap-based buffer over-read exists in Sass::Prelexer::skip_over_scopes in prelexer.hpp when called from Sass::Parser::parse_import(), a similar issue to CVE-2018-11693.
<p>Publish Date: 2019-01-14
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-6286>CVE-2019-6286</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-6286 (Medium) detected in node-sass-v4.11.0 - ## CVE-2019-6286 - Medium Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.11.0</b></p></summary>
<p>
<p>:rainbow: Node.js bindings to libsass</p>
<p>Library home page: <a href=https://github.com/sass/node-sass.git>https://github.com/sass/node-sass.git</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Library Source Files (128)</summary>
<p></p>
<p> * The source files were matched to this source library based on a best effort match. Source libraries are selected from a list of probable public libraries.</p>
<p>
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/libsass/src/to_value.hpp
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/libsass/src/source_map.cpp
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/src/constants.hpp
- /Cordova-Examples/ionic_openwhisk/node_modules/node-sass/src/libsass/src/to_c.hpp
- /Cordova-Examples/ionicWeatherV2/node_modules/node-sass/src/libsass/src/node.hpp
- /Cordova-Examples/fixcontacts/node_modules/node-sass/src/libsass/src/memory_manager.hpp
- /Cordova-Examples/db2/node_modules/node-sass/src/libsass/src/expand.cpp
- /Cordova-Examples/ionicauth2/node_modules/node-sass/src/libsass/src/listize.cpp
- /Cordova-Examples/fixcontacts/node_modules/node-sass/src/libsass/src/output.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/lib/extensions.js
- /Cordova-Examples/ionicauth2/node_modules/node-sass/src/libsass/src/parser.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/backtrace.hpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/units.hpp
- /Cordova-Examples/ionicWeatherV2/node_modules/node-sass/src/libsass/test/test_node.cpp
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/sass_types/number.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/scripts/build.js
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/custom_importer_bridge.cpp
- /Cordova-Examples/ionicAuth2Social/node_modules/node-sass/src/libsass/src/sass_util.hpp
- /Cordova-Examples/db1/node_modules/node-sass/src/sass_types/sass_value_wrapper.h
- /Cordova-Examples/db2/node_modules/node-sass/src/sass_types/string.cpp
- /Cordova-Examples/db1/node_modules/node-sass/src/sass_types/null.cpp
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/contrib/plugin.cpp
- /Cordova-Examples/ionicWeatherV2/node_modules/node-sass/src/libsass/src/listize.hpp
- /Cordova-Examples/ionicAuth2Social/node_modules/node-sass/src/libsass/src/lexer.hpp
- /Cordova-Examples/sidemenudemo/node_modules/node-sass/src/libsass/src/sass_util.cpp
- /Cordova-Examples/db2/node_modules/node-sass/src/libsass/test/test_superselector.cpp
- /Cordova-Examples/fixcontacts/node_modules/node-sass/src/libsass/src/units.cpp
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/src/cencode.c
- /Cordova-Examples/db3/node_modules/node-sass/src/libsass/src/ast_factory.hpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/sass_functions.cpp
- /Cordova-Examples/ionicauth2/node_modules/node-sass/src/libsass/src/ast.hpp
- /Cordova-Examples/sidemenudemo/node_modules/node-sass/src/libsass/src/remove_placeholders.hpp
- /Cordova-Examples/db2/node_modules/node-sass/src/libsass/src/utf8_string.hpp
- /Cordova-Examples/db3/node_modules/node-sass/src/libsass/src/memory_manager.cpp
- /Cordova-Examples/ionic_openwhisk/node_modules/node-sass/src/libsass/src/sass_values.cpp
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/callback_bridge.h
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/test/cli.js
- /Cordova-Examples/ionicWeatherV2/node_modules/node-sass/src/libsass/src/constants.cpp
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/libsass/src/to_c.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/test/lowlevel.js
- /Cordova-Examples/sidemenudemo/node_modules/node-sass/src/libsass/src/remove_placeholders.cpp
- /Cordova-Examples/db3/node_modules/node-sass/src/sass_types/color.cpp
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/libsass/src/util.cpp
- /Cordova-Examples/ionicWeatherV2/node_modules/node-sass/src/libsass/src/eval.cpp
- /Cordova-Examples/ionicAuth2Social/node_modules/node-sass/src/libsass/src/sass_context.hpp
- /Cordova-Examples/ionic_openwhisk/node_modules/node-sass/src/libsass/src/output.hpp
- /Cordova-Examples/sidemenudemo/node_modules/node-sass/src/libsass/src/operation.hpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/lib/render.js
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/custom_function_bridge.cpp
- /Cordova-Examples/db1/node_modules/node-sass/src/libsass/src/inspect.hpp
- /Cordova-Examples/ionicauth2/node_modules/node-sass/src/libsass/src/sass.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/test/errors.js
- /Cordova-Examples/ionic_openwhisk/node_modules/node-sass/src/libsass/src/file.hpp
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/libsass/include/sass/values.h
- /Cordova-Examples/db1/node_modules/node-sass/src/libsass/src/paths.hpp
- /Cordova-Examples/ionic_openwhisk/node_modules/node-sass/src/libsass/src/sass_values.hpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/lib/errors.js
- /Cordova-Examples/ionic_openwhisk/node_modules/node-sass/src/sass_types/boolean.h
- /Cordova-Examples/sidemenudemo/node_modules/node-sass/src/libsass/src/error_handling.hpp
- /Cordova-Examples/fixcontacts/node_modules/node-sass/src/libsass/test/test_unification.cpp
- /Cordova-Examples/sidemenudemo/node_modules/node-sass/src/libsass/src/sass.hpp
- /Cordova-Examples/ionicAuth2Social/node_modules/node-sass/src/sass_types/list.h
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/file.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/scripts/coverage.js
- /Cordova-Examples/ionicAuth2Social/node_modules/node-sass/src/libsass/src/position.cpp
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/src/expand.hpp
- /Cordova-Examples/ionicWeatherV2/node_modules/node-sass/src/libsass/src/context.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/prelexer.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/inspect.cpp
- /Cordova-Examples/db3/node_modules/node-sass/src/libsass/src/extend.cpp
- /Cordova-Examples/ionic_openwhisk/node_modules/node-sass/src/libsass/src/parser.hpp
- /Cordova-Examples/ionicWeatherV2/node_modules/node-sass/src/sass_types/list.cpp
- /Cordova-Examples/db3/node_modules/node-sass/src/libsass/src/bind.cpp
- /Cordova-Examples/fixcontacts/node_modules/node-sass/src/sass_types/map.cpp
- /Cordova-Examples/ionic_openwhisk/node_modules/node-sass/src/libsass/src/sass_context.cpp
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/src/values.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/test/api.js
- /Cordova-Examples/ionicWeatherV2/node_modules/node-sass/src/libsass/src/emitter.cpp
- /Cordova-Examples/ionicauth2/node_modules/node-sass/src/libsass/src/debugger.hpp
- /Cordova-Examples/fixcontacts/node_modules/node-sass/src/libsass/src/ast_fwd_decl.hpp
- /Cordova-Examples/ionic_openwhisk/node_modules/node-sass/src/libsass/src/util.hpp
- /Cordova-Examples/db3/node_modules/node-sass/src/libsass/src/cssize.cpp
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/sass_context_wrapper.cpp
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/src/error_handling.cpp
- /Cordova-Examples/ionicauth2/node_modules/node-sass/src/libsass/src/position.hpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/test/spec.js
- /Cordova-Examples/ionicauth2/node_modules/node-sass/src/libsass/src/ast_def_macros.hpp
- /Cordova-Examples/fixcontacts/node_modules/node-sass/src/libsass/src/emitter.hpp
- /Cordova-Examples/fixcontacts/node_modules/node-sass/src/libsass/src/eval.hpp
- /Cordova-Examples/db1/node_modules/node-sass/src/libsass/src/sass2scss.cpp
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/src/functions.cpp
- /Cordova-Examples/db1/node_modules/node-sass/src/libsass/src/functions.hpp
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/libsass/src/prelexer.hpp
- /Cordova-Examples/ionicauth2/node_modules/node-sass/src/sass_types/boolean.cpp
- /Cordova-Examples/ionicWeatherV2/node_modules/node-sass/src/custom_importer_bridge.h
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/libsass/src/ast.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/utf8_string.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/include/sass/functions.h
- /Cordova-Examples/fixcontacts/node_modules/node-sass/src/libsass/src/lexer.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/test/runtime.js
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/scripts/install.js
- /Cordova-Examples/db3/node_modules/node-sass/src/sass_context_wrapper.h
- /Cordova-Examples/sidemenudemo/node_modules/node-sass/src/libsass/src/b64/encode.h
- /Cordova-Examples/db2/node_modules/node-sass/src/libsass/src/base64vlq.cpp
- /Cordova-Examples/ionic_openwhisk/node_modules/node-sass/src/libsass/src/to_value.cpp
- /Cordova-Examples/db2/node_modules/node-sass/src/libsass/src/cssize.hpp
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/src/environment.cpp
- /Cordova-Examples/sidemenudemo/node_modules/node-sass/src/libsass/src/c99func.c
- /Cordova-Examples/fixcontacts/node_modules/node-sass/src/libsass/test/test_subset_map.cpp
- /Cordova-Examples/sidemenudemo/node_modules/node-sass/src/libsass/src/subset_map.hpp
- /Cordova-Examples/db3/node_modules/node-sass/src/libsass/include/sass/base.h
- /Cordova-Examples/ionicWeatherV2/node_modules/node-sass/src/binding.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/source_map.hpp
- /Cordova-Examples/db1/node_modules/node-sass/src/libsass/include/sass2scss.h
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/libsass/src/plugins.cpp
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/src/extend.hpp
- /Cordova-Examples/sidemenudemo/node_modules/node-sass/src/libsass/src/node.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/plugins.hpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/lib/index.js
- /Cordova-Examples/ionicAuth2Social/node_modules/node-sass/src/libsass/src/environment.hpp
- /Cordova-Examples/ionicweatherv3/node_modules/node-sass/src/libsass/include/sass/context.h
- /Cordova-Examples/ionicAuth2Social/node_modules/node-sass/src/sass_types/color.h
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/src/color_maps.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/json.cpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/debug.hpp
- /Cordova-Examples/fixcontacts2a/node_modules/node-sass/src/libsass/src/context.hpp
- /Cordova-Examples/ionicauth2/node_modules/node-sass/src/sass_types/factory.cpp
- /Cordova-Examples/ionic_intl/node_modules/node-sass/src/libsass/src/color_maps.hpp
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass 3.5.5, a heap-based buffer over-read exists in Sass::Prelexer::skip_over_scopes in prelexer.hpp when called from Sass::Parser::parse_import(), a similar issue to CVE-2018-11693.
<p>Publish Date: 2019-01-14
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-6286>CVE-2019-6286</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in node sass cve medium severity vulnerability vulnerable library node rainbow node js bindings to libsass library home page a href library source files the source files were matched to this source library based on a best effort match source libraries are selected from a list of probable public libraries cordova examples node modules node sass src libsass src to value hpp cordova examples node modules node sass src libsass src source map cpp cordova examples ionic intl node modules node sass src libsass src constants hpp cordova examples ionic openwhisk node modules node sass src libsass src to c hpp cordova examples node modules node sass src libsass src node hpp cordova examples fixcontacts node modules node sass src libsass src memory manager hpp cordova examples node modules node sass src libsass src expand cpp cordova examples node modules node sass src libsass src listize cpp cordova examples fixcontacts node modules node sass src libsass src output cpp cordova examples node modules node sass lib extensions js cordova examples node modules node sass src libsass src parser cpp cordova examples node modules node sass src libsass src backtrace hpp cordova examples node modules node sass src libsass src units hpp cordova examples node modules node sass src libsass test test node cpp cordova examples node modules node sass src sass types number cpp cordova examples node modules node sass scripts build js cordova examples node modules node sass src custom importer bridge cpp cordova examples node modules node sass src libsass src sass util hpp cordova examples node modules node sass src sass types sass value wrapper h cordova examples node modules node sass src sass types string cpp cordova examples node modules node sass src sass types null cpp cordova examples ionic intl node modules node sass src libsass contrib plugin cpp cordova examples node modules node sass src libsass src listize hpp cordova examples node modules node sass src libsass src lexer hpp cordova examples sidemenudemo node modules node sass src libsass src sass util cpp cordova examples node modules node sass src libsass test test superselector cpp cordova examples fixcontacts node modules node sass src libsass src units cpp cordova examples ionic intl node modules node sass src libsass src cencode c cordova examples node modules node sass src libsass src ast factory hpp cordova examples node modules node sass src libsass src sass functions cpp cordova examples node modules node sass src libsass src ast hpp cordova examples sidemenudemo node modules node sass src libsass src remove placeholders hpp cordova examples node modules node sass src libsass src string hpp cordova examples node modules node sass src libsass src memory manager cpp cordova examples ionic openwhisk node modules node sass src libsass src sass values cpp cordova examples node modules node sass src callback bridge h cordova examples node modules node sass test cli js cordova examples node modules node sass src libsass src constants cpp cordova examples node modules node sass src libsass src to c cpp cordova examples node modules node sass test lowlevel js cordova examples sidemenudemo node modules node sass src libsass src remove placeholders cpp cordova examples node modules node sass src sass types color cpp cordova examples node modules node sass src libsass src util cpp cordova examples node modules node sass src libsass src eval cpp cordova examples node modules node sass src libsass src sass context hpp cordova examples ionic openwhisk node modules node sass src libsass src output hpp cordova examples sidemenudemo node modules node sass src libsass src operation hpp cordova examples node modules node sass lib render js cordova examples node modules node sass src custom function bridge cpp cordova examples node modules node sass src libsass src inspect hpp cordova examples node modules node sass src libsass src sass cpp cordova examples node modules node sass test errors js cordova examples ionic openwhisk node modules node sass src libsass src file hpp cordova examples node modules node sass src libsass include sass values h cordova examples node modules node sass src libsass src paths hpp cordova examples ionic openwhisk node modules node sass src libsass src sass values hpp cordova examples node modules node sass lib errors js cordova examples ionic openwhisk node modules node sass src sass types boolean h cordova examples sidemenudemo node modules node sass src libsass src error handling hpp cordova examples fixcontacts node modules node sass src libsass test test unification cpp cordova examples sidemenudemo node modules node sass src libsass src sass hpp cordova examples node modules node sass src sass types list h cordova examples node modules node sass src libsass src file cpp cordova examples node modules node sass scripts coverage js cordova examples node modules node sass src libsass src position cpp cordova examples ionic intl node modules node sass src libsass src expand hpp cordova examples node modules node sass src libsass src context cpp cordova examples node modules node sass src libsass src prelexer cpp cordova examples node modules node sass src libsass src inspect cpp cordova examples node modules node sass src libsass src extend cpp cordova examples ionic openwhisk node modules node sass src libsass src parser hpp cordova examples node modules node sass src sass types list cpp cordova examples node modules node sass src libsass src bind cpp cordova examples fixcontacts node modules node sass src sass types map cpp cordova examples ionic openwhisk node modules node sass src libsass src sass context cpp cordova examples ionic intl node modules node sass src libsass src values cpp cordova examples node modules node sass test api js cordova examples node modules node sass src libsass src emitter cpp cordova examples node modules node sass src libsass src debugger hpp cordova examples fixcontacts node modules node sass src libsass src ast fwd decl hpp cordova examples ionic openwhisk node modules node sass src libsass src util hpp cordova examples node modules node sass src libsass src cssize cpp cordova examples node modules node sass src sass context wrapper cpp cordova examples ionic intl node modules node sass src libsass src error handling cpp cordova examples node modules node sass src libsass src position hpp cordova examples node modules node sass test spec js cordova examples node modules node sass src libsass src ast def macros hpp cordova examples fixcontacts node modules node sass src libsass src emitter hpp cordova examples fixcontacts node modules node sass src libsass src eval hpp cordova examples node modules node sass src libsass src cpp cordova examples ionic intl node modules node sass src libsass src functions cpp cordova examples node modules node sass src libsass src functions hpp cordova examples node modules node sass src libsass src prelexer hpp cordova examples node modules node sass src sass types boolean cpp cordova examples node modules node sass src custom importer bridge h cordova examples node modules node sass src libsass src ast cpp cordova examples node modules node sass src libsass src string cpp cordova examples node modules node sass src libsass include sass functions h cordova examples fixcontacts node modules node sass src libsass src lexer cpp cordova examples node modules node sass test runtime js cordova examples node modules node sass scripts install js cordova examples node modules node sass src sass context wrapper h cordova examples sidemenudemo node modules node sass src libsass src encode h cordova examples node modules node sass src libsass src cpp cordova examples ionic openwhisk node modules node sass src libsass src to value cpp cordova examples node modules node sass src libsass src cssize hpp cordova examples ionic intl node modules node sass src libsass src environment cpp cordova examples sidemenudemo node modules node sass src libsass src c cordova examples fixcontacts node modules node sass src libsass test test subset map cpp cordova examples sidemenudemo node modules node sass src libsass src subset map hpp cordova examples node modules node sass src libsass include sass base h cordova examples node modules node sass src binding cpp cordova examples node modules node sass src libsass src source map hpp cordova examples node modules node sass src libsass include h cordova examples node modules node sass src libsass src plugins cpp cordova examples ionic intl node modules node sass src libsass src extend hpp cordova examples sidemenudemo node modules node sass src libsass src node cpp cordova examples node modules node sass src libsass src plugins hpp cordova examples node modules node sass lib index js cordova examples node modules node sass src libsass src environment hpp cordova examples node modules node sass src libsass include sass context h cordova examples node modules node sass src sass types color h cordova examples ionic intl node modules node sass src libsass src color maps cpp cordova examples node modules node sass src libsass src json cpp cordova examples node modules node sass src libsass src debug hpp cordova examples node modules node sass src libsass src context hpp cordova examples node modules node sass src sass types factory cpp cordova examples ionic intl node modules node sass src libsass src color maps hpp vulnerability details in libsass a heap based buffer over read exists in sass prelexer skip over scopes in prelexer hpp when called from sass parser parse import a similar issue to cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href step up your open source security game with whitesource | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.