Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
185,030 | 21,785,054,121 | IssuesEvent | 2022-05-14 02:18:41 | Yash-Handa/GitHub-Org-Geographics | https://api.github.com/repos/Yash-Handa/GitHub-Org-Geographics | closed | WS-2021-0153 (High) detected in ejs-2.7.4.tgz - autoclosed | security vulnerability | ## WS-2021-0153 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ejs-2.7.4.tgz</b></p></summary>
<p>Embedded JavaScript templates</p>
<p>Library home page: <a href="https://registry.npmjs.org/ejs/-/ejs-2.7.4.tgz">https://registry.npmjs.org/ejs/-/ejs-2.7.4.tgz</a></p>
<p>Path to dependency file: GitHub-Org-Geographics/package.json</p>
<p>Path to vulnerable library: GitHub-Org-Geographics/node_modules/ejs/package.json</p>
<p>
Dependency Hierarchy:
- webpack-cli-4.0.0.tgz (Root Library)
- init-1.1.3.tgz
- generators-1.3.1.tgz
- yeoman-environment-2.10.3.tgz
- mem-fs-editor-6.0.0.tgz
- :x: **ejs-2.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Yash-Handa/GitHub-Org-Geographics/commit/2afbaa3b97ca67f2d9d19b0e7a6ea74e98f38bb7">2afbaa3b97ca67f2d9d19b0e7a6ea74e98f38bb7</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Arbitrary Code Injection vulnerability was found in ejs before 3.1.6. Caused by filename which isn't sanitized for display.
<p>Publish Date: 2021-01-22
<p>URL: <a href=https://github.com/mde/ejs/commit/abaee2be937236b1b8da9a1f55096c17dda905fd>WS-2021-0153</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mde/ejs/issues/571">https://github.com/mde/ejs/issues/571</a></p>
<p>Release Date: 2021-01-22</p>
<p>Fix Resolution: ejs - 3.1.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2021-0153 (High) detected in ejs-2.7.4.tgz - autoclosed - ## WS-2021-0153 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ejs-2.7.4.tgz</b></p></summary>
<p>Embedded JavaScript templates</p>
<p>Library home page: <a href="https://registry.npmjs.org/ejs/-/ejs-2.7.4.tgz">https://registry.npmjs.org/ejs/-/ejs-2.7.4.tgz</a></p>
<p>Path to dependency file: GitHub-Org-Geographics/package.json</p>
<p>Path to vulnerable library: GitHub-Org-Geographics/node_modules/ejs/package.json</p>
<p>
Dependency Hierarchy:
- webpack-cli-4.0.0.tgz (Root Library)
- init-1.1.3.tgz
- generators-1.3.1.tgz
- yeoman-environment-2.10.3.tgz
- mem-fs-editor-6.0.0.tgz
- :x: **ejs-2.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Yash-Handa/GitHub-Org-Geographics/commit/2afbaa3b97ca67f2d9d19b0e7a6ea74e98f38bb7">2afbaa3b97ca67f2d9d19b0e7a6ea74e98f38bb7</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Arbitrary Code Injection vulnerability was found in ejs before 3.1.6. Caused by filename which isn't sanitized for display.
<p>Publish Date: 2021-01-22
<p>URL: <a href=https://github.com/mde/ejs/commit/abaee2be937236b1b8da9a1f55096c17dda905fd>WS-2021-0153</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mde/ejs/issues/571">https://github.com/mde/ejs/issues/571</a></p>
<p>Release Date: 2021-01-22</p>
<p>Fix Resolution: ejs - 3.1.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws high detected in ejs tgz autoclosed ws high severity vulnerability vulnerable library ejs tgz embedded javascript templates library home page a href path to dependency file github org geographics package json path to vulnerable library github org geographics node modules ejs package json dependency hierarchy webpack cli tgz root library init tgz generators tgz yeoman environment tgz mem fs editor tgz x ejs tgz vulnerable library found in head commit a href vulnerability details arbitrary code injection vulnerability was found in ejs before caused by filename which isn t sanitized for display publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ejs step up your open source security game with whitesource | 0 |
8,387 | 4,235,262,217 | IssuesEvent | 2016-07-05 14:42:27 | blairconrad/FakeItEasy | https://api.github.com/repos/blairconrad/FakeItEasy | closed | 996.996.983-beta001 release | build documentation P2 | **in-progress** when all other issues on this milestone are closed.
- [ ] run code analysis in VS in *Release* mode and address violations (send a regular PR which must be merged before continuing)
- [ ] if necessary, change `VERSION_SUFFIX` on the [CI Server](http://teamcity.codebetter.com/admin/editBuildParams.html?id=buildType:bt929)
to appropriate "-beta123" or "" (for non-betas) value and initiate a build
- [ ] check build
- edit draft release in [GitHub UI](https://github.com/FakeItEasy/FakeItEasy/releases):
- [ ] complete release notes, mentioning non-owner contributors, if any (move release notes forward from any pre-releases to the current release)
- [ ] attach nupkg(s) - main package and/or analyzer, whichever have new content
- [ ] publish the release
- [ ] push NuGet package
- [ ] de-list pre-release or superseded buggy NuGet packages if present
- [ ] update website with contributors list (if in place)
- [ ] tweet, mentioning contributors and post link as comment here for easy retweeting ;-)
- [ ] post tweet in [Gitter](https://gitter.im/FakeItEasy/FakeItEasy)
- [ ] post links to the NuGet and GitHub release in each issue in this milestone, with thanks to contributors
- if there's to be a new pre-release issue
- [ ] run `rake pre_release[version_suffix]` to create a new draft GitHub Release and a new issue (like this one) for the next release, adding it to the current milestone
- [ ] change `VERSION_SUFFIX` on the [CI Server](http://teamcity.codebetter.com/admin/editBuildParams.html?id=buildType:bt929)
- [ ] close this milestone | 1.0 | 996.996.983-beta001 release - **in-progress** when all other issues on this milestone are closed.
- [ ] run code analysis in VS in *Release* mode and address violations (send a regular PR which must be merged before continuing)
- [ ] if necessary, change `VERSION_SUFFIX` on the [CI Server](http://teamcity.codebetter.com/admin/editBuildParams.html?id=buildType:bt929)
to appropriate "-beta123" or "" (for non-betas) value and initiate a build
- [ ] check build
- edit draft release in [GitHub UI](https://github.com/FakeItEasy/FakeItEasy/releases):
- [ ] complete release notes, mentioning non-owner contributors, if any (move release notes forward from any pre-releases to the current release)
- [ ] attach nupkg(s) - main package and/or analyzer, whichever have new content
- [ ] publish the release
- [ ] push NuGet package
- [ ] de-list pre-release or superseded buggy NuGet packages if present
- [ ] update website with contributors list (if in place)
- [ ] tweet, mentioning contributors and post link as comment here for easy retweeting ;-)
- [ ] post tweet in [Gitter](https://gitter.im/FakeItEasy/FakeItEasy)
- [ ] post links to the NuGet and GitHub release in each issue in this milestone, with thanks to contributors
- if there's to be a new pre-release issue
- [ ] run `rake pre_release[version_suffix]` to create a new draft GitHub Release and a new issue (like this one) for the next release, adding it to the current milestone
- [ ] change `VERSION_SUFFIX` on the [CI Server](http://teamcity.codebetter.com/admin/editBuildParams.html?id=buildType:bt929)
- [ ] close this milestone | non_priority | release in progress when all other issues on this milestone are closed run code analysis in vs in release mode and address violations send a regular pr which must be merged before continuing if necessary change version suffix on the to appropriate or for non betas value and initiate a build check build edit draft release in complete release notes mentioning non owner contributors if any move release notes forward from any pre releases to the current release attach nupkg s main package and or analyzer whichever have new content publish the release push nuget package de list pre release or superseded buggy nuget packages if present update website with contributors list if in place tweet mentioning contributors and post link as comment here for easy retweeting post tweet in post links to the nuget and github release in each issue in this milestone with thanks to contributors if there s to be a new pre release issue run rake pre release to create a new draft github release and a new issue like this one for the next release adding it to the current milestone change version suffix on the close this milestone | 0 |
121,416 | 15,931,465,053 | IssuesEvent | 2021-04-14 03:25:49 | microsoft/BotFramework-Composer | https://api.github.com/repos/microsoft/BotFramework-Composer | closed | New UI on Skills page for enabling / disabling skill and managing allowed callers list | P1 Team: Authoring UX Design feature-request | ## Is your feature request related to a problem? Please describe.
We need to provide users of Composer the ability to manage the following via the UI.
- The new IsSkill setting introduced into the SDK, to indicate if a bot should allow itself to be consumed as a skill.
- The AllowedCallers list
The runtime changes related to this are currently in PR https://github.com/microsoft/BotFramework-Composer/pull/4086
## Describe the solution you'd like
The agreement amongst the team who met to discuss this was that the existing skills page within Composer would be altered to include both the IsSkill toggle and UI to allow a user to manage the Allowed Callers list.
By default the IsSkill toggle will be set to false. A user should be able to enable this toggle on the skills page, or have this turned on automatically if the user creates a skill manifest.
The Allowed Callers UI should allow a user to indicate all callers should be allowed (this should be the default) or that a specified list of app Ids should be allowed. | 1.0 | New UI on Skills page for enabling / disabling skill and managing allowed callers list - ## Is your feature request related to a problem? Please describe.
We need to provide users of Composer the ability to manage the following via the UI.
- The new IsSkill setting introduced into the SDK, to indicate if a bot should allow itself to be consumed as a skill.
- The AllowedCallers list
The runtime changes related to this are currently in PR https://github.com/microsoft/BotFramework-Composer/pull/4086
## Describe the solution you'd like
The agreement amongst the team who met to discuss this was that the existing skills page within Composer would be altered to include both the IsSkill toggle and UI to allow a user to manage the Allowed Callers list.
By default the IsSkill toggle will be set to false. A user should be able to enable this toggle on the skills page, or have this turned on automatically if the user creates a skill manifest.
The Allowed Callers UI should allow a user to indicate all callers should be allowed (this should be the default) or that a specified list of app Ids should be allowed. | non_priority | new ui on skills page for enabling disabling skill and managing allowed callers list is your feature request related to a problem please describe we need to provide users of composer the ability to manage the following via the ui the new isskill setting introduced into the sdk to indicate if a bot should allow itself to be consumed as a skill the allowedcallers list the runtime changes related to this are currently in pr describe the solution you d like the agreement amongst the team who met to discuss this was that the existing skills page within composer would be altered to include both the isskill toggle and ui to allow a user to manage the allowed callers list by default the isskill toggle will be set to false a user should be able to enable this toggle on the skills page or have this turned on automatically if the user creates a skill manifest the allowed callers ui should allow a user to indicate all callers should be allowed this should be the default or that a specified list of app ids should be allowed | 0 |
125,058 | 17,795,930,535 | IssuesEvent | 2021-08-31 22:13:20 | ghc-dev/Ashley-Campos | https://api.github.com/repos/ghc-dev/Ashley-Campos | opened | CVE-2019-5413 (High) detected in morgan-1.6.1.tgz | security vulnerability | ## CVE-2019-5413 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>morgan-1.6.1.tgz</b></p></summary>
<p>HTTP request logger middleware for node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/morgan/-/morgan-1.6.1.tgz">https://registry.npmjs.org/morgan/-/morgan-1.6.1.tgz</a></p>
<p>Path to dependency file: Ashley-Campos/package.json</p>
<p>Path to vulnerable library: /node_modules/morgan/package.json</p>
<p>
Dependency Hierarchy:
- :x: **morgan-1.6.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Ashley-Campos/commit/93bde7a441bf435e2b02a4e5c2c7e6e2e2ebb8e0">93bde7a441bf435e2b02a4e5c2c7e6e2e2ebb8e0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An attacker can use the format parameter to inject arbitrary commands in the npm package morgan < 1.9.1.
<p>Publish Date: 2019-03-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-5413>CVE-2019-5413</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://hackerone.com/reports/390881">https://hackerone.com/reports/390881</a></p>
<p>Release Date: 2019-03-21</p>
<p>Fix Resolution: 1.9.1</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"morgan","packageVersion":"1.6.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"morgan:1.6.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.9.1"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-5413","vulnerabilityDetails":"An attacker can use the format parameter to inject arbitrary commands in the npm package morgan \u003c 1.9.1.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-5413","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2019-5413 (High) detected in morgan-1.6.1.tgz - ## CVE-2019-5413 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>morgan-1.6.1.tgz</b></p></summary>
<p>HTTP request logger middleware for node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/morgan/-/morgan-1.6.1.tgz">https://registry.npmjs.org/morgan/-/morgan-1.6.1.tgz</a></p>
<p>Path to dependency file: Ashley-Campos/package.json</p>
<p>Path to vulnerable library: /node_modules/morgan/package.json</p>
<p>
Dependency Hierarchy:
- :x: **morgan-1.6.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Ashley-Campos/commit/93bde7a441bf435e2b02a4e5c2c7e6e2e2ebb8e0">93bde7a441bf435e2b02a4e5c2c7e6e2e2ebb8e0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An attacker can use the format parameter to inject arbitrary commands in the npm package morgan < 1.9.1.
<p>Publish Date: 2019-03-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-5413>CVE-2019-5413</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://hackerone.com/reports/390881">https://hackerone.com/reports/390881</a></p>
<p>Release Date: 2019-03-21</p>
<p>Fix Resolution: 1.9.1</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"morgan","packageVersion":"1.6.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"morgan:1.6.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.9.1"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-5413","vulnerabilityDetails":"An attacker can use the format parameter to inject arbitrary commands in the npm package morgan \u003c 1.9.1.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-5413","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in morgan tgz cve high severity vulnerability vulnerable library morgan tgz http request logger middleware for node js library home page a href path to dependency file ashley campos package json path to vulnerable library node modules morgan package json dependency hierarchy x morgan tgz vulnerable library found in head commit a href found in base branch master vulnerability details an attacker can use the format parameter to inject arbitrary commands in the npm package morgan publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree morgan isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails an attacker can use the format parameter to inject arbitrary commands in the npm package morgan vulnerabilityurl | 0 |
307,620 | 26,547,145,253 | IssuesEvent | 2023-01-20 01:59:33 | andymina/seam-carving | https://api.github.com/repos/andymina/seam-carving | closed | Adopt GoogleTest as the main unit-testing framework | tests | [doctest](https://github.com/doctest/doctest) is great for a simplified version of Catch2, but it doesn't have great support for value-parameterized testing which is a necessity since the addition of #38.
GoogleTest seems to have a fairly straightforward way of implementing value-parameterized tests ([example here](https://blog.andreiavram.ro/gtest-parameterized-tests-json/)). | 1.0 | Adopt GoogleTest as the main unit-testing framework - [doctest](https://github.com/doctest/doctest) is great for a simplified version of Catch2, but it doesn't have great support for value-parameterized testing which is a necessity since the addition of #38.
GoogleTest seems to have a fairly straightforward way of implementing value-parameterized tests ([example here](https://blog.andreiavram.ro/gtest-parameterized-tests-json/)). | non_priority | adopt googletest as the main unit testing framework is great for a simplified version of but it doesn t have great support for value parameterized testing which is a necessity since the addition of googletest seems to have a fairly straightforward way of implementing value parameterized tests | 0 |
272,017 | 29,794,973,172 | IssuesEvent | 2023-06-16 01:01:05 | billmcchesney1/singleton | https://api.github.com/repos/billmcchesney1/singleton | closed | WS-2019-0490 (High) detected in jcommander-1.35.jar - autoclosed | Mend: dependency security vulnerability | ## WS-2019-0490 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jcommander-1.35.jar</b></p></summary>
<p>A Java framework to parse command line options with annotations.</p>
<p>Library home page: <a href="http://beust.com/">http://beust.com/</a></p>
<p>Path to dependency file: /g11n-ws/vip-manager-lite-i18n/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.beust/jcommander/1.35/47592e181b0bdbbeb63029e08c5e74f6803c4edd/jcommander-1.35.jar</p>
<p>
Dependency Hierarchy:
- asciidoctorj-1.5.6.jar (Root Library)
- :x: **jcommander-1.35.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/billmcchesney1/singleton/commit/2bb883ae0b199f3e432621e91d0f801cfc406a89">2bb883ae0b199f3e432621e91d0f801cfc406a89</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Inclusion of Functionality from Untrusted Control Sphere vulnerability found in jcommander before 1.75. jcommander resolving dependencies over HTTP instead of HTTPS.
<p>Publish Date: 2019-02-19
<p>URL: <a href=https://github.com/cbeust/jcommander/commit/3ae95595febbed9c13f367b6bda5c0be1c572c53>WS-2019-0490</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-02-19</p>
<p>Fix Resolution (com.beust:jcommander): 1.75</p>
<p>Direct dependency fix Resolution (org.asciidoctor:asciidoctorj): 2.3.1</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | True | WS-2019-0490 (High) detected in jcommander-1.35.jar - autoclosed - ## WS-2019-0490 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jcommander-1.35.jar</b></p></summary>
<p>A Java framework to parse command line options with annotations.</p>
<p>Library home page: <a href="http://beust.com/">http://beust.com/</a></p>
<p>Path to dependency file: /g11n-ws/vip-manager-lite-i18n/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.beust/jcommander/1.35/47592e181b0bdbbeb63029e08c5e74f6803c4edd/jcommander-1.35.jar</p>
<p>
Dependency Hierarchy:
- asciidoctorj-1.5.6.jar (Root Library)
- :x: **jcommander-1.35.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/billmcchesney1/singleton/commit/2bb883ae0b199f3e432621e91d0f801cfc406a89">2bb883ae0b199f3e432621e91d0f801cfc406a89</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Inclusion of Functionality from Untrusted Control Sphere vulnerability found in jcommander before 1.75. jcommander resolving dependencies over HTTP instead of HTTPS.
<p>Publish Date: 2019-02-19
<p>URL: <a href=https://github.com/cbeust/jcommander/commit/3ae95595febbed9c13f367b6bda5c0be1c572c53>WS-2019-0490</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-02-19</p>
<p>Fix Resolution (com.beust:jcommander): 1.75</p>
<p>Direct dependency fix Resolution (org.asciidoctor:asciidoctorj): 2.3.1</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | non_priority | ws high detected in jcommander jar autoclosed ws high severity vulnerability vulnerable library jcommander jar a java framework to parse command line options with annotations library home page a href path to dependency file ws vip manager lite build gradle path to vulnerable library home wss scanner gradle caches modules files com beust jcommander jcommander jar dependency hierarchy asciidoctorj jar root library x jcommander jar vulnerable library found in head commit a href found in base branch master vulnerability details inclusion of functionality from untrusted control sphere vulnerability found in jcommander before jcommander resolving dependencies over http instead of https publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution com beust jcommander direct dependency fix resolution org asciidoctor asciidoctorj rescue worker helmet automatic remediation is available for this issue | 0 |
103,197 | 11,348,892,157 | IssuesEvent | 2020-01-24 02:14:32 | hackforla/record-clearance | https://api.github.com/repos/hackforla/record-clearance | closed | Update Project Page & board - Record Clearance | documentation | ### Overview
Update all pages of this branch with project names and goals.
### Action Items
- [x] Replace text-holder on read me page
- [x] Add Agenda & meeting notes
- [x] Move the rest of the documents from [branch](https://github.com/H1Angela/record-clearance) to the master
### Resources/Instructions
[Branch](https://github.com/H1Angela/record-clearance)
| 1.0 | Update Project Page & board - Record Clearance - ### Overview
Update all pages of this branch with project names and goals.
### Action Items
- [x] Replace text-holder on read me page
- [x] Add Agenda & meeting notes
- [x] Move the rest of the documents from [branch](https://github.com/H1Angela/record-clearance) to the master
### Resources/Instructions
[Branch](https://github.com/H1Angela/record-clearance)
| non_priority | update project page board record clearance overview update all pages of this branch with project names and goals action items replace text holder on read me page add agenda meeting notes move the rest of the documents from to the master resources instructions | 0 |
399,738 | 27,253,470,126 | IssuesEvent | 2023-02-22 09:50:01 | chill-viking/ng-libs | https://api.github.com/repos/chill-viking/ng-libs | closed | chore(workflows): improve workflows | documentation :writing_hand: non-functional improvement :tada: | ### Description
Create singular workflow with multiple jobs, multiple workflows are frustrating
- end up confused about failures after reviewing a workflow run (takes to filtered results for that workflow alone, instead of all workflows)
- can improve performance (have initial job that does caching so that all other jobs use cache instead of all jobs installing dependencies at once)
- publish build artefact for reuse in deployment jobs
### Sample of Change
Reuse workflows in singular workflow. Figure out approach to check if changes found in specific folders.
### Additional Context
_No response_
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct | 1.0 | chore(workflows): improve workflows - ### Description
Create singular workflow with multiple jobs, multiple workflows are frustrating
- end up confused about failures after reviewing a workflow run (takes to filtered results for that workflow alone, instead of all workflows)
- can improve performance (have initial job that does caching so that all other jobs use cache instead of all jobs installing dependencies at once)
- publish build artefact for reuse in deployment jobs
### Sample of Change
Reuse workflows in singular workflow. Figure out approach to check if changes found in specific folders.
### Additional Context
_No response_
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct | non_priority | chore workflows improve workflows description create singular workflow with multiple jobs multiple workflows are frustrating end up confused about failures after reviewing a workflow run takes to filtered results for that workflow alone instead of all workflows can improve performance have initial job that does caching so that all other jobs use cache instead of all jobs installing dependencies at once publish build artefact for reuse in deployment jobs sample of change reuse workflows in singular workflow figure out approach to check if changes found in specific folders additional context no response code of conduct i agree to follow this project s code of conduct | 0 |
275,665 | 23,929,169,359 | IssuesEvent | 2022-09-10 09:07:10 | secretlint/secretlint | https://api.github.com/repos/secretlint/secretlint | closed | Add tests for secretlint --init | good first issue Status: PR Welcome Type: Testing | We need to write tests for `secretlint --init`.
Also, add test for config-creator package. | 1.0 | Add tests for secretlint --init - We need to write tests for `secretlint --init`.
Also, add test for config-creator package. | non_priority | add tests for secretlint init we need to write tests for secretlint init also add test for config creator package | 0 |
263,386 | 28,030,095,604 | IssuesEvent | 2023-03-28 11:49:35 | RG4421/ampere-centos-kernel | https://api.github.com/repos/RG4421/ampere-centos-kernel | reopened | CVE-2020-15780 (Medium) detected in linuxv5.2 | Mend: dependency security vulnerability | ## CVE-2020-15780 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv5.2</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/torvalds/linux.git>https://github.com/torvalds/linux.git</a></p>
<p>Found in base branch: <b>amp-centos-8.0-kernel</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/acpi/acpi_configfs.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/acpi/acpi_configfs.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/acpi/acpi_configfs.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in drivers/acpi/acpi_configfs.c in the Linux kernel before 5.7.7. Injection of malicious ACPI tables via configfs could be used by attackers to bypass lockdown and secure boot restrictions, aka CID-75b0cea7bf30.
<p>Publish Date: 2020-07-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-15780>CVE-2020-15780</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-15780">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-15780</a></p>
<p>Release Date: 2020-07-15</p>
<p>Fix Resolution: v5.8-rc3</p>
</p>
</details>
<p></p>
| True | CVE-2020-15780 (Medium) detected in linuxv5.2 - ## CVE-2020-15780 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv5.2</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/torvalds/linux.git>https://github.com/torvalds/linux.git</a></p>
<p>Found in base branch: <b>amp-centos-8.0-kernel</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/acpi/acpi_configfs.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/acpi/acpi_configfs.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/acpi/acpi_configfs.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in drivers/acpi/acpi_configfs.c in the Linux kernel before 5.7.7. Injection of malicious ACPI tables via configfs could be used by attackers to bypass lockdown and secure boot restrictions, aka CID-75b0cea7bf30.
<p>Publish Date: 2020-07-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-15780>CVE-2020-15780</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-15780">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-15780</a></p>
<p>Release Date: 2020-07-15</p>
<p>Fix Resolution: v5.8-rc3</p>
</p>
</details>
<p></p>
| non_priority | cve medium detected in cve medium severity vulnerability vulnerable library linux kernel source tree library home page a href found in base branch amp centos kernel vulnerable source files drivers acpi acpi configfs c drivers acpi acpi configfs c drivers acpi acpi configfs c vulnerability details an issue was discovered in drivers acpi acpi configfs c in the linux kernel before injection of malicious acpi tables via configfs could be used by attackers to bypass lockdown and secure boot restrictions aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution | 0 |
14,786 | 3,886,294,317 | IssuesEvent | 2016-04-14 00:02:41 | DarkEnergyScienceCollaboration/Twinkles | https://api.github.com/repos/DarkEnergyScienceCollaboration/Twinkles | opened | Database plan | Documentation Epic: L2 Database | In response to the DB epic in #191: we need to start a simple markdown document, and use it to sketch as succinctly as possible our database needs for Run 1.1, Run 2 and Twinkles 2, so that we can communicate well with our colleagues at SLAC and NERSC (ie so we can send them a URL and ask for feedback). I'll make a stub and then pass it on! | 1.0 | Database plan - In response to the DB epic in #191: we need to start a simple markdown document, and use it to sketch as succinctly as possible our database needs for Run 1.1, Run 2 and Twinkles 2, so that we can communicate well with our colleagues at SLAC and NERSC (ie so we can send them a URL and ask for feedback). I'll make a stub and then pass it on! | non_priority | database plan in response to the db epic in we need to start a simple markdown document and use it to sketch as succinctly as possible our database needs for run run and twinkles so that we can communicate well with our colleagues at slac and nersc ie so we can send them a url and ask for feedback i ll make a stub and then pass it on | 0 |
16,674 | 21,778,528,717 | IssuesEvent | 2022-05-13 16:05:28 | camunda/zeebe | https://api.github.com/repos/camunda/zeebe | closed | MetricsExporter does not configure a record filter | kind/bug scope/broker area/performance area/reliability team/process-automation | **Describe the bug**
<!-- A clear and concise description of what the bug is. -->
The [MetricsExporter](https://github.com/camunda/zeebe/blob/8.0.0/broker/src/main/java/io/camunda/zeebe/broker/exporter/metrics/MetricsExporter.java#L27) does not override the [configure](https://github.com/camunda/zeebe/blob/8.0.0/exporter-api/src/main/java/io/camunda/zeebe/exporter/api/Exporter.java#L43) method. This method allows to set a filter for which records are available to export. Since the MetricsExporter only exports records of a few value types (i.e. JOB, JOB_BATCH, PROCESS_INSTANCE), it unnecessarily reads the record values of all other records.
This can completely halt exporting on a partition when combined with #6442.
**To Reproduce**
<!--
Steps to reproduce the behavior
If possible add a minimal reproducer code sample
- when using the Java client: https://github.com/zeebe-io/zeebe-test-template-java
-->
- configure the MetricsExporter for the broker
- run the broker
- deploy a very large process with mistakes that lead to zeebe rejecting the deployment with validation errors
- note that the exporter stops making progress
- note an increase in CPU because it keeps trying to re-read the record value indefinitely
**Expected behavior**
<!-- A clear and concise description of what you expected to happen. -->
The metrics exporter should be configured in such a way that only those records that it wants to export are actually read from the log by the exporter director.
**Log/Stacktrace**
<!-- If possible add the full stacktrace or Zeebe log which contains the issue. -->
<details><summary>Full Stacktrace</summary>
<p>
```
java.lang.IllegalArgumentException: invalid offset: -31808
at org.agrona.concurrent.UnsafeBuffer.boundsCheckWrap(UnsafeBuffer.java:2425) ~[agrona-1.15.0.jar:1.15.0]
at org.agrona.concurrent.UnsafeBuffer.wrap(UnsafeBuffer.java:277) ~[agrona-1.15.0.jar:1.15.0]
at io.camunda.zeebe.msgpack.spec.MsgPackReader.wrap(MsgPackReader.java:49) ~[zeebe-msgpack-core-8.0.0.jar:8.0.0]
at io.camunda.zeebe.msgpack.UnpackedObject.wrap(UnpackedObject.java:30) ~[zeebe-msgpack-value-8.0.0.jar:8.0.0]
at io.camunda.zeebe.logstreams.impl.log.LoggedEventImpl.readValue(LoggedEventImpl.java:135) ~[zeebe-logstreams-8.0.0.jar:8.0.0]
at io.camunda.zeebe.engine.processing.streamprocessor.RecordValues.readRecordValue(RecordValues.java:35) ~[zeebe-workflow-engine-8.0.0.jar:8.0.0]
at io.camunda.zeebe.broker.exporter.stream.ExporterDirector$RecordExporter.wrap(ExporterDirector.java:489) ~[zeebe-broker-8.0.0.jar:8.0.0]
at io.camunda.zeebe.broker.exporter.stream.ExporterDirector.lambda$exportEvent$9(ExporterDirector.java:391) ~[zeebe-broker-8.0.0.jar:8.0.0]
at io.camunda.zeebe.util.retry.ActorRetryMechanism.run(ActorRetryMechanism.java:36) ~[zeebe-util-8.0.0.jar:8.0.0]
at io.camunda.zeebe.util.retry.EndlessRetryStrategy.run(EndlessRetryStrategy.java:50) ~[zeebe-util-8.0.0.jar:8.0.0]
at io.camunda.zeebe.util.sched.ActorJob.invoke(ActorJob.java:79) ~[zeebe-util-8.0.0.jar:8.0.0]
at io.camunda.zeebe.util.sched.ActorJob.execute(ActorJob.java:44) ~[zeebe-util-8.0.0.jar:8.0.0]
at io.camunda.zeebe.util.sched.ActorTask.execute(ActorTask.java:122) ~[zeebe-util-8.0.0.jar:8.0.0]
at io.camunda.zeebe.util.sched.ActorThread.executeCurrentTask(ActorThread.java:97) ~[zeebe-util-8.0.0.jar:8.0.0]
at io.camunda.zeebe.util.sched.ActorThread.doWork(ActorThread.java:80) ~[zeebe-util-8.0.0.jar:8.0.0]
at io.camunda.zeebe.util.sched.ActorThread.run(ActorThread.java:189) ~[zeebe-util-8.0.0.jar:8.0.0]
```
</p>
</details>
**Environment:**
- Zeebe Version: 8.0
- Configuration: MetricsExporter
| 1.0 | MetricsExporter does not configure a record filter - **Describe the bug**
<!-- A clear and concise description of what the bug is. -->
The [MetricsExporter](https://github.com/camunda/zeebe/blob/8.0.0/broker/src/main/java/io/camunda/zeebe/broker/exporter/metrics/MetricsExporter.java#L27) does not override the [configure](https://github.com/camunda/zeebe/blob/8.0.0/exporter-api/src/main/java/io/camunda/zeebe/exporter/api/Exporter.java#L43) method. This method allows to set a filter for which records are available to export. Since the MetricsExporter only exports records of a few value types (i.e. JOB, JOB_BATCH, PROCESS_INSTANCE), it unnecessarily reads the record values of all other records.
This can completely halt exporting on a partition when combined with #6442.
**To Reproduce**
<!--
Steps to reproduce the behavior
If possible add a minimal reproducer code sample
- when using the Java client: https://github.com/zeebe-io/zeebe-test-template-java
-->
- configure the MetricsExporter for the broker
- run the broker
- deploy a very large process with mistakes that lead to zeebe rejecting the deployment with validation errors
- note that the exporter stops making progress
- note an increase in CPU because it keeps trying to re-read the record value indefinitely
**Expected behavior**
<!-- A clear and concise description of what you expected to happen. -->
The metrics exporter should be configured in such a way that only those records that it wants to export are actually read from the log by the exporter director.
**Log/Stacktrace**
<!-- If possible add the full stacktrace or Zeebe log which contains the issue. -->
<details><summary>Full Stacktrace</summary>
<p>
```
java.lang.IllegalArgumentException: invalid offset: -31808
at org.agrona.concurrent.UnsafeBuffer.boundsCheckWrap(UnsafeBuffer.java:2425) ~[agrona-1.15.0.jar:1.15.0]
at org.agrona.concurrent.UnsafeBuffer.wrap(UnsafeBuffer.java:277) ~[agrona-1.15.0.jar:1.15.0]
at io.camunda.zeebe.msgpack.spec.MsgPackReader.wrap(MsgPackReader.java:49) ~[zeebe-msgpack-core-8.0.0.jar:8.0.0]
at io.camunda.zeebe.msgpack.UnpackedObject.wrap(UnpackedObject.java:30) ~[zeebe-msgpack-value-8.0.0.jar:8.0.0]
at io.camunda.zeebe.logstreams.impl.log.LoggedEventImpl.readValue(LoggedEventImpl.java:135) ~[zeebe-logstreams-8.0.0.jar:8.0.0]
at io.camunda.zeebe.engine.processing.streamprocessor.RecordValues.readRecordValue(RecordValues.java:35) ~[zeebe-workflow-engine-8.0.0.jar:8.0.0]
at io.camunda.zeebe.broker.exporter.stream.ExporterDirector$RecordExporter.wrap(ExporterDirector.java:489) ~[zeebe-broker-8.0.0.jar:8.0.0]
at io.camunda.zeebe.broker.exporter.stream.ExporterDirector.lambda$exportEvent$9(ExporterDirector.java:391) ~[zeebe-broker-8.0.0.jar:8.0.0]
at io.camunda.zeebe.util.retry.ActorRetryMechanism.run(ActorRetryMechanism.java:36) ~[zeebe-util-8.0.0.jar:8.0.0]
at io.camunda.zeebe.util.retry.EndlessRetryStrategy.run(EndlessRetryStrategy.java:50) ~[zeebe-util-8.0.0.jar:8.0.0]
at io.camunda.zeebe.util.sched.ActorJob.invoke(ActorJob.java:79) ~[zeebe-util-8.0.0.jar:8.0.0]
at io.camunda.zeebe.util.sched.ActorJob.execute(ActorJob.java:44) ~[zeebe-util-8.0.0.jar:8.0.0]
at io.camunda.zeebe.util.sched.ActorTask.execute(ActorTask.java:122) ~[zeebe-util-8.0.0.jar:8.0.0]
at io.camunda.zeebe.util.sched.ActorThread.executeCurrentTask(ActorThread.java:97) ~[zeebe-util-8.0.0.jar:8.0.0]
at io.camunda.zeebe.util.sched.ActorThread.doWork(ActorThread.java:80) ~[zeebe-util-8.0.0.jar:8.0.0]
at io.camunda.zeebe.util.sched.ActorThread.run(ActorThread.java:189) ~[zeebe-util-8.0.0.jar:8.0.0]
```
</p>
</details>
**Environment:**
- Zeebe Version: 8.0
- Configuration: MetricsExporter
| non_priority | metricsexporter does not configure a record filter describe the bug the does not override the method this method allows to set a filter for which records are available to export since the metricsexporter only exports records of a few value types i e job job batch process instance it unnecessarily reads the record values of all other records this can completely halt exporting on a partition when combined with to reproduce steps to reproduce the behavior if possible add a minimal reproducer code sample when using the java client configure the metricsexporter for the broker run the broker deploy a very large process with mistakes that lead to zeebe rejecting the deployment with validation errors note that the exporter stops making progress note an increase in cpu because it keeps trying to re read the record value indefinitely expected behavior the metrics exporter should be configured in such a way that only those records that it wants to export are actually read from the log by the exporter director log stacktrace full stacktrace java lang illegalargumentexception invalid offset at org agrona concurrent unsafebuffer boundscheckwrap unsafebuffer java at org agrona concurrent unsafebuffer wrap unsafebuffer java at io camunda zeebe msgpack spec msgpackreader wrap msgpackreader java at io camunda zeebe msgpack unpackedobject wrap unpackedobject java at io camunda zeebe logstreams impl log loggedeventimpl readvalue loggedeventimpl java at io camunda zeebe engine processing streamprocessor recordvalues readrecordvalue recordvalues java at io camunda zeebe broker exporter stream exporterdirector recordexporter wrap exporterdirector java at io camunda zeebe broker exporter stream exporterdirector lambda exportevent exporterdirector java at io camunda zeebe util retry actorretrymechanism run actorretrymechanism java at io camunda zeebe util retry endlessretrystrategy run endlessretrystrategy java at io camunda zeebe util sched actorjob invoke actorjob java at io camunda zeebe util sched actorjob execute actorjob java at io camunda zeebe util sched actortask execute actortask java at io camunda zeebe util sched actorthread executecurrenttask actorthread java at io camunda zeebe util sched actorthread dowork actorthread java at io camunda zeebe util sched actorthread run actorthread java environment zeebe version configuration metricsexporter | 0 |
231,683 | 17,703,575,982 | IssuesEvent | 2021-08-25 03:18:55 | serilog-contrib/SerilogSinksInMemory | https://api.github.com/repos/serilog-contrib/SerilogSinksInMemory | opened | Add Serilog Sinks icon to Serilog.Sinks.InMemory NuGet package | documentation | The Serilog.Sinks.InMemory NuGet pacackage doesn't have an icon yet.

I suggest using the standard icon for sinks:

| 1.0 | Add Serilog Sinks icon to Serilog.Sinks.InMemory NuGet package - The Serilog.Sinks.InMemory NuGet pacackage doesn't have an icon yet.

I suggest using the standard icon for sinks:

| non_priority | add serilog sinks icon to serilog sinks inmemory nuget package the serilog sinks inmemory nuget pacackage doesn t have an icon yet i suggest using the standard icon for sinks | 0 |
120,922 | 12,100,621,287 | IssuesEvent | 2020-04-20 14:04:00 | scikit-image/scikit-image | https://api.github.com/repos/scikit-image/scikit-image | closed | Add examples to docstring for structuring elements to visualize the shape | good first issue type: documentation | ## Description
Add examples to show for each of these functions:
* [ ] skimage.morphology.square(width[, dtype])
* [ ] skimage.morphology.rectangle(width, height)
* [ ] skimage.morphology.diamond(radius[, dtype])
* [ ] skimage.morphology.disk(radius[, dtype])
* [ ] skimage.morphology.cube(width[, dtype])
* [ ] skimage.morphology.octahedron(radius[, dtype])
* [ ] skimage.morphology.ball(radius[, dtype])
* [ ] skimage.morphology.octagon(m, n[, dtype])
* [ ] skimage.morphology.star(a[, dtype])
the typical shape of the structuring element.
Cc ( @emmanuelle : another first issue idea).
| 1.0 | Add examples to docstring for structuring elements to visualize the shape - ## Description
Add examples to show for each of these functions:
* [ ] skimage.morphology.square(width[, dtype])
* [ ] skimage.morphology.rectangle(width, height)
* [ ] skimage.morphology.diamond(radius[, dtype])
* [ ] skimage.morphology.disk(radius[, dtype])
* [ ] skimage.morphology.cube(width[, dtype])
* [ ] skimage.morphology.octahedron(radius[, dtype])
* [ ] skimage.morphology.ball(radius[, dtype])
* [ ] skimage.morphology.octagon(m, n[, dtype])
* [ ] skimage.morphology.star(a[, dtype])
the typical shape of the structuring element.
Cc ( @emmanuelle : another first issue idea).
| non_priority | add examples to docstring for structuring elements to visualize the shape description add examples to show for each of these functions skimage morphology square width skimage morphology rectangle width height skimage morphology diamond radius skimage morphology disk radius skimage morphology cube width skimage morphology octahedron radius skimage morphology ball radius skimage morphology octagon m n skimage morphology star a the typical shape of the structuring element cc emmanuelle another first issue idea | 0 |
9,283 | 6,198,859,789 | IssuesEvent | 2017-07-05 20:11:01 | flutter/flutter-intellij | https://api.github.com/repos/flutter/flutter-intellij | closed | Confusion around `pub get` prompt | bug dependency: dart plugin topic-daily-work usability | Sometimes, after updating pubspec.yaml in IntelliJ, we just see the Dart banner prompting to update dependencies. The Flutter banner w/ slightly different appearance and wording ("Get Dependencies") never displays.
My understanding is the vanilla Dart version of the command (`pub get`) is not exactly equivalent to `flutter packages get` which aside from the UX inconsistency, might be a more serious issue.
## Steps to Reproduce
1. Open pubspec.yaml, either in IntelliJ or in a text editor.
1. Make edits and switch to main.dart in IntelliJ.
1. Sometimes get Dart version of the "update dependencies" banner in IntelliJ, rather than the Flutter version (which is not exactly equivalent).
## Version info
This behavior was seen on the I/O kiosks.
flutter doctor output (from non-kiosk environment):
```
[✓] Flutter (on Mac OS X 10.12.4 16E195, channel master)
• Flutter at /Users/jackson/git/flutter
• Framework revision 7154ac48db (4 hours ago), 2017-05-16 09:32:27 -0700
• Engine revision 6fef702cfa
• Tools Dart version 1.23.0-dev.11.11
[✓] Android toolchain - develop for Android devices (Android SDK 25.0.3)
• Android SDK at /Users/jackson/Library/Android/sdk/
• Platform android-25, build-tools 25.0.3
• ANDROID_HOME = /Users/jackson/Library/Android/sdk/
• Java binary at: /Applications/Android Studio.app/Contents/jre/jdk/Contents/Home/bin/java
• Java version: OpenJDK Runtime Environment (build 1.8.0_112-release-b06)
[✓] iOS toolchain - develop for iOS devices (Xcode 8.3.1)
• Xcode at /Applications/Xcode.app/Contents/Developer
• Xcode 8.3.1, Build version 8E1000a
• ios-deploy 1.9.1
• CocoaPods version 1.0.1
[✓] Android Studio (version 2.3)
• Android Studio at /Applications/Android Studio.app/Contents
• Gradle version 3.2
• Java version: OpenJDK Runtime Environment (build 1.8.0_112-release-b06)
[✓] IntelliJ IDEA Community Edition (version 2016.3.4)
• Dart plugin version 163.13137
• Flutter plugin version 12.1
[✓] Connected devices
• iPhone 7 Plus • 5F90A4C3-6F80-446A-88CB-5394635BF8EF • ios • iOS 10.3 (simulator)
```
@collinjackson | True | Confusion around `pub get` prompt - Sometimes, after updating pubspec.yaml in IntelliJ, we just see the Dart banner prompting to update dependencies. The Flutter banner w/ slightly different appearance and wording ("Get Dependencies") never displays.
My understanding is the vanilla Dart version of the command (`pub get`) is not exactly equivalent to `flutter packages get` which aside from the UX inconsistency, might be a more serious issue.
## Steps to Reproduce
1. Open pubspec.yaml, either in IntelliJ or in a text editor.
1. Make edits and switch to main.dart in IntelliJ.
1. Sometimes get Dart version of the "update dependencies" banner in IntelliJ, rather than the Flutter version (which is not exactly equivalent).
## Version info
This behavior was seen on the I/O kiosks.
flutter doctor output (from non-kiosk environment):
```
[✓] Flutter (on Mac OS X 10.12.4 16E195, channel master)
• Flutter at /Users/jackson/git/flutter
• Framework revision 7154ac48db (4 hours ago), 2017-05-16 09:32:27 -0700
• Engine revision 6fef702cfa
• Tools Dart version 1.23.0-dev.11.11
[✓] Android toolchain - develop for Android devices (Android SDK 25.0.3)
• Android SDK at /Users/jackson/Library/Android/sdk/
• Platform android-25, build-tools 25.0.3
• ANDROID_HOME = /Users/jackson/Library/Android/sdk/
• Java binary at: /Applications/Android Studio.app/Contents/jre/jdk/Contents/Home/bin/java
• Java version: OpenJDK Runtime Environment (build 1.8.0_112-release-b06)
[✓] iOS toolchain - develop for iOS devices (Xcode 8.3.1)
• Xcode at /Applications/Xcode.app/Contents/Developer
• Xcode 8.3.1, Build version 8E1000a
• ios-deploy 1.9.1
• CocoaPods version 1.0.1
[✓] Android Studio (version 2.3)
• Android Studio at /Applications/Android Studio.app/Contents
• Gradle version 3.2
• Java version: OpenJDK Runtime Environment (build 1.8.0_112-release-b06)
[✓] IntelliJ IDEA Community Edition (version 2016.3.4)
• Dart plugin version 163.13137
• Flutter plugin version 12.1
[✓] Connected devices
• iPhone 7 Plus • 5F90A4C3-6F80-446A-88CB-5394635BF8EF • ios • iOS 10.3 (simulator)
```
@collinjackson | non_priority | confusion around pub get prompt sometimes after updating pubspec yaml in intellij we just see the dart banner prompting to update dependencies the flutter banner w slightly different appearance and wording get dependencies never displays my understanding is the vanilla dart version of the command pub get is not exactly equivalent to flutter packages get which aside from the ux inconsistency might be a more serious issue steps to reproduce open pubspec yaml either in intellij or in a text editor make edits and switch to main dart in intellij sometimes get dart version of the update dependencies banner in intellij rather than the flutter version which is not exactly equivalent version info this behavior was seen on the i o kiosks flutter doctor output from non kiosk environment flutter on mac os x channel master • flutter at users jackson git flutter • framework revision hours ago • engine revision • tools dart version dev android toolchain develop for android devices android sdk • android sdk at users jackson library android sdk • platform android build tools • android home users jackson library android sdk • java binary at applications android studio app contents jre jdk contents home bin java • java version openjdk runtime environment build release ios toolchain develop for ios devices xcode • xcode at applications xcode app contents developer • xcode build version • ios deploy • cocoapods version android studio version • android studio at applications android studio app contents • gradle version • java version openjdk runtime environment build release intellij idea community edition version • dart plugin version • flutter plugin version connected devices • iphone plus • • ios • ios simulator collinjackson | 0 |
51,969 | 7,740,179,255 | IssuesEvent | 2018-05-28 19:59:58 | KenSuenobu/scattersphere | https://api.github.com/repos/KenSuenobu/scattersphere | opened | Add RetryableTask | documentation enhancement good first issue help wanted | Add the ability for a `RunnableTask` to be retried if a failure occurs. Failures on some `RunnableTask`s can be transient errors (network down, file not found, etc), so this option needs to be available. | 1.0 | Add RetryableTask - Add the ability for a `RunnableTask` to be retried if a failure occurs. Failures on some `RunnableTask`s can be transient errors (network down, file not found, etc), so this option needs to be available. | non_priority | add retryabletask add the ability for a runnabletask to be retried if a failure occurs failures on some runnabletask s can be transient errors network down file not found etc so this option needs to be available | 0 |
244,293 | 26,375,080,862 | IssuesEvent | 2023-01-12 01:16:39 | DaemonToolz/locuste.dashboard.ui | https://api.github.com/repos/DaemonToolz/locuste.dashboard.ui | opened | WS-2023-0004 (Medium) detected in jszip-3.3.0.tgz | security vulnerability | ## WS-2023-0004 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jszip-3.3.0.tgz</b></p></summary>
<p>Create, read and edit .zip files with JavaScript http://stuartk.com/jszip</p>
<p>Library home page: <a href="https://registry.npmjs.org/jszip/-/jszip-3.3.0.tgz">https://registry.npmjs.org/jszip/-/jszip-3.3.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/jszip/package.json</p>
<p>
Dependency Hierarchy:
- protractor-5.4.3.tgz (Root Library)
- selenium-webdriver-3.6.0.tgz
- :x: **jszip-3.3.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jszip before 3.8.0 does not sanitize filenames when files are loaded with `loadAsync`, which makes the library vunerable to zip-slip attack.
<p>Publish Date: 2023-01-04
<p>URL: <a href=https://github.com/Stuk/jszip/commit/2edab366119c9ee948357c02f1206c28566cdf15>WS-2023-0004</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2023-01-04</p>
<p>Fix Resolution (jszip): 3.6.0</p>
<p>Direct dependency fix Resolution (protractor): 5.4.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2023-0004 (Medium) detected in jszip-3.3.0.tgz - ## WS-2023-0004 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jszip-3.3.0.tgz</b></p></summary>
<p>Create, read and edit .zip files with JavaScript http://stuartk.com/jszip</p>
<p>Library home page: <a href="https://registry.npmjs.org/jszip/-/jszip-3.3.0.tgz">https://registry.npmjs.org/jszip/-/jszip-3.3.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/jszip/package.json</p>
<p>
Dependency Hierarchy:
- protractor-5.4.3.tgz (Root Library)
- selenium-webdriver-3.6.0.tgz
- :x: **jszip-3.3.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jszip before 3.8.0 does not sanitize filenames when files are loaded with `loadAsync`, which makes the library vunerable to zip-slip attack.
<p>Publish Date: 2023-01-04
<p>URL: <a href=https://github.com/Stuk/jszip/commit/2edab366119c9ee948357c02f1206c28566cdf15>WS-2023-0004</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2023-01-04</p>
<p>Fix Resolution (jszip): 3.6.0</p>
<p>Direct dependency fix Resolution (protractor): 5.4.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in jszip tgz ws medium severity vulnerability vulnerable library jszip tgz create read and edit zip files with javascript library home page a href path to dependency file package json path to vulnerable library node modules jszip package json dependency hierarchy protractor tgz root library selenium webdriver tgz x jszip tgz vulnerable library vulnerability details jszip before does not sanitize filenames when files are loaded with loadasync which makes the library vunerable to zip slip attack publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution jszip direct dependency fix resolution protractor step up your open source security game with mend | 0 |
101,195 | 16,493,367,601 | IssuesEvent | 2021-05-25 07:38:57 | benchmarkdebricked/angular | https://api.github.com/repos/benchmarkdebricked/angular | opened | CVE-2021-23358 (High) detected in underscore-1.6.0.tgz | security vulnerability | ## CVE-2021-23358 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>underscore-1.6.0.tgz</b></p></summary>
<p>JavaScript's functional programming helper library.</p>
<p>Library home page: <a href="https://registry.npmjs.org/underscore/-/underscore-1.6.0.tgz">https://registry.npmjs.org/underscore/-/underscore-1.6.0.tgz</a></p>
<p>Path to dependency file: angular/aio/package.json</p>
<p>Path to vulnerable library: angular/aio/node_modules/underscore</p>
<p>
Dependency Hierarchy:
- lighthouse-4.3.0.tgz (Root Library)
- jsonlint-mod-1.7.4.tgz
- nomnom-1.8.1.tgz
- :x: **underscore-1.6.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/benchmarkdebricked/angular/commit/69ad0ced6b2b3ebe8f9d4d3b9dda14051592bbdf">69ad0ced6b2b3ebe8f9d4d3b9dda14051592bbdf</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Injection via the template function, particularly when a variable property is passed as an argument as it is not sanitized.
<p>Publish Date: 2021-03-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358>CVE-2021-23358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358</a></p>
<p>Release Date: 2021-03-29</p>
<p>Fix Resolution: underscore - 1.12.1,1.13.0-2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-23358 (High) detected in underscore-1.6.0.tgz - ## CVE-2021-23358 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>underscore-1.6.0.tgz</b></p></summary>
<p>JavaScript's functional programming helper library.</p>
<p>Library home page: <a href="https://registry.npmjs.org/underscore/-/underscore-1.6.0.tgz">https://registry.npmjs.org/underscore/-/underscore-1.6.0.tgz</a></p>
<p>Path to dependency file: angular/aio/package.json</p>
<p>Path to vulnerable library: angular/aio/node_modules/underscore</p>
<p>
Dependency Hierarchy:
- lighthouse-4.3.0.tgz (Root Library)
- jsonlint-mod-1.7.4.tgz
- nomnom-1.8.1.tgz
- :x: **underscore-1.6.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/benchmarkdebricked/angular/commit/69ad0ced6b2b3ebe8f9d4d3b9dda14051592bbdf">69ad0ced6b2b3ebe8f9d4d3b9dda14051592bbdf</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Injection via the template function, particularly when a variable property is passed as an argument as it is not sanitized.
<p>Publish Date: 2021-03-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358>CVE-2021-23358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358</a></p>
<p>Release Date: 2021-03-29</p>
<p>Fix Resolution: underscore - 1.12.1,1.13.0-2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in underscore tgz cve high severity vulnerability vulnerable library underscore tgz javascript s functional programming helper library library home page a href path to dependency file angular aio package json path to vulnerable library angular aio node modules underscore dependency hierarchy lighthouse tgz root library jsonlint mod tgz nomnom tgz x underscore tgz vulnerable library found in head commit a href vulnerability details the package underscore from and before from and before are vulnerable to arbitrary code injection via the template function particularly when a variable property is passed as an argument as it is not sanitized publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution underscore step up your open source security game with whitesource | 0 |
36,251 | 6,521,838,234 | IssuesEvent | 2017-08-28 22:22:43 | NAVADMC/ADSM | https://api.github.com/repos/NAVADMC/ADSM | closed | Fix Unhelpful help text | Documentation | While working on #245 I've noticed places with unhelpful help text:
- Destruction capacity - The relational function used to define the daily destruction capacity.
- X and Y axis labels would be more useful
- Units detected before triggering vaccination - The number of clinical Units which must be detected before the initiation of a vaccination program.
- I think this prevents any vaccinations from happening before the "vaccination program". Does it start up instantly?
- Vaccination capacity - Relational function used to define the daily vaccination capacity.
- What variable/events does this actually affect in the simulation?
- Test Delay - Function that describes the delay in obtaining test results.
- This is a PDF... so I may be able to deduce the Y axis is a percentage and that this is a distribution of possible values for "delay". But I have to pause and really think about that because the help text says nothing about the "distribution of delays"
- Zone direct movement - Function the describes direct movement rate. (and indirect)
- It's not immediately obvious that this is our "Quarantine" option as "Quarantine" does not appear anywhere in the program. Some thing like "Models imperfect Quarantine as a percentage of normal Direct Movement in days since the Zone was first established."
Is there a "Documentation Person" I can assign these to?
| 1.0 | Fix Unhelpful help text - While working on #245 I've noticed places with unhelpful help text:
- Destruction capacity - The relational function used to define the daily destruction capacity.
- X and Y axis labels would be more useful
- Units detected before triggering vaccination - The number of clinical Units which must be detected before the initiation of a vaccination program.
- I think this prevents any vaccinations from happening before the "vaccination program". Does it start up instantly?
- Vaccination capacity - Relational function used to define the daily vaccination capacity.
- What variable/events does this actually affect in the simulation?
- Test Delay - Function that describes the delay in obtaining test results.
- This is a PDF... so I may be able to deduce the Y axis is a percentage and that this is a distribution of possible values for "delay". But I have to pause and really think about that because the help text says nothing about the "distribution of delays"
- Zone direct movement - Function the describes direct movement rate. (and indirect)
- It's not immediately obvious that this is our "Quarantine" option as "Quarantine" does not appear anywhere in the program. Some thing like "Models imperfect Quarantine as a percentage of normal Direct Movement in days since the Zone was first established."
Is there a "Documentation Person" I can assign these to?
| non_priority | fix unhelpful help text while working on i ve noticed places with unhelpful help text destruction capacity the relational function used to define the daily destruction capacity x and y axis labels would be more useful units detected before triggering vaccination the number of clinical units which must be detected before the initiation of a vaccination program i think this prevents any vaccinations from happening before the vaccination program does it start up instantly vaccination capacity relational function used to define the daily vaccination capacity what variable events does this actually affect in the simulation test delay function that describes the delay in obtaining test results this is a pdf so i may be able to deduce the y axis is a percentage and that this is a distribution of possible values for delay but i have to pause and really think about that because the help text says nothing about the distribution of delays zone direct movement function the describes direct movement rate and indirect it s not immediately obvious that this is our quarantine option as quarantine does not appear anywhere in the program some thing like models imperfect quarantine as a percentage of normal direct movement in days since the zone was first established is there a documentation person i can assign these to | 0 |
8,897 | 12,400,969,348 | IssuesEvent | 2020-05-21 08:56:11 | goharbor/harbor | https://api.github.com/repos/goharbor/harbor | opened | [Requirement] Support multiple conditions to query audit logs | kind/requirement | I want to query the audit logs for a certain reousrce on a specific action. For example query all users who pull the artifact library/hello-world.
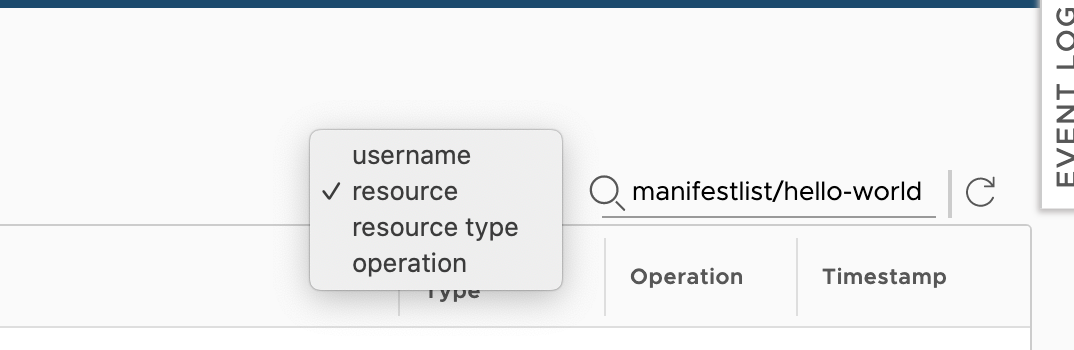
| 1.0 | [Requirement] Support multiple conditions to query audit logs - I want to query the audit logs for a certain reousrce on a specific action. For example query all users who pull the artifact library/hello-world.
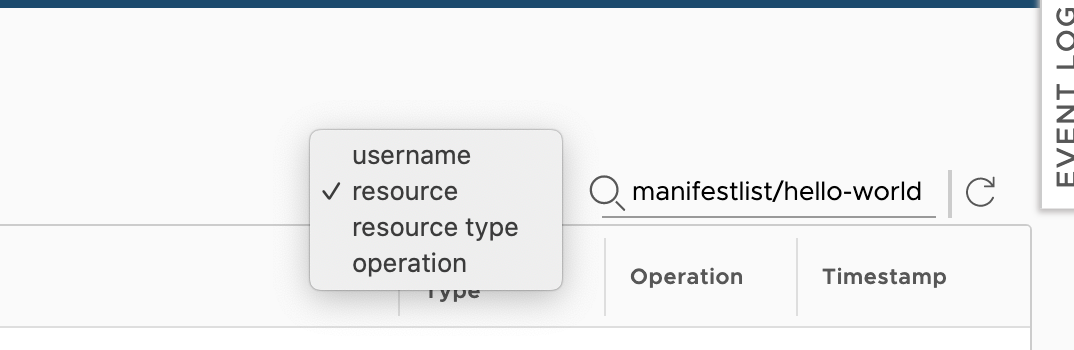
| non_priority | support multiple conditions to query audit logs i want to query the audit logs for a certain reousrce on a specific action for example query all users who pull the artifact library hello world | 0 |
1,004 | 4,794,374,346 | IssuesEvent | 2016-10-31 20:50:54 | almighty/almighty-ui | https://api.github.com/repos/almighty/almighty-ui | opened | Apply AOT | architecture | Set up and configure Ahead of Time compilation to improve performance.
This should be done through webpack. | 1.0 | Apply AOT - Set up and configure Ahead of Time compilation to improve performance.
This should be done through webpack. | non_priority | apply aot set up and configure ahead of time compilation to improve performance this should be done through webpack | 0 |
74,485 | 7,431,213,867 | IssuesEvent | 2018-03-25 12:34:16 | nodejs/node | https://api.github.com/repos/nodejs/node | closed | Flaky parallel/test-http-url.parse-auth | CI / flaky test http test | https://ci.nodejs.org/job/node-test-commit-linux/16299/nodes=debian8-x86/console
```
not ok 831 parallel/test-http-url.parse-auth
---
duration_ms: 0.169
severity: fail
stack: |-
```
Ping @nodejs/http2 @nodejs/http | 2.0 | Flaky parallel/test-http-url.parse-auth - https://ci.nodejs.org/job/node-test-commit-linux/16299/nodes=debian8-x86/console
```
not ok 831 parallel/test-http-url.parse-auth
---
duration_ms: 0.169
severity: fail
stack: |-
```
Ping @nodejs/http2 @nodejs/http | non_priority | flaky parallel test http url parse auth not ok parallel test http url parse auth duration ms severity fail stack ping nodejs nodejs http | 0 |
334,982 | 24,448,409,810 | IssuesEvent | 2022-10-06 20:09:24 | OBOFoundry/OBOFoundry.github.io | https://api.github.com/repos/OBOFoundry/OBOFoundry.github.io | closed | Custom pages in GitHub Pages should be used for 404s | website documentation usability feature attn: Technical WG | Given that there are many URLs in the wild like
http://www.obofoundry.org/cgi-bin/detail.cgi?id=brenda ,
it would be best to configure the GitHub Pages 404s to either contain a search, an explanation and link, or to forward to the top-level page with a warning.
E.g.: https://help.github.com/articles/creating-a-custom-404-page-for-your-github-pages-site/ | 1.0 | Custom pages in GitHub Pages should be used for 404s - Given that there are many URLs in the wild like
http://www.obofoundry.org/cgi-bin/detail.cgi?id=brenda ,
it would be best to configure the GitHub Pages 404s to either contain a search, an explanation and link, or to forward to the top-level page with a warning.
E.g.: https://help.github.com/articles/creating-a-custom-404-page-for-your-github-pages-site/ | non_priority | custom pages in github pages should be used for given that there are many urls in the wild like it would be best to configure the github pages to either contain a search an explanation and link or to forward to the top level page with a warning e g | 0 |
15,737 | 5,169,921,757 | IssuesEvent | 2017-01-18 03:10:19 | bitshares/bitshares-core | https://api.github.com/repos/bitshares/bitshares-core | closed | Intermittent connection failure in app_test | review-existing-code | _From @theoreticalbts on July 14, 2015 22:24_
After fixing generally obsolete `app_test` in cfd9dd0f75270f01c4d28b717e9117b732b63801 I notice that every few runs, I get the following error:
```
$ sudo -u graphene -H tests/app_test --log_level=message
Running 1 test case...
Creating temporary files
Creating and initializing app1
Creating and initializing app2
Starting app1 and waiting 500 ms
1209829ms th_a application.cpp:190 operator() ] Initializing database...
1209838ms th_a application.cpp:63 create_example_genes ] Allocating all stake to 5KQwrPbwdL6PhXujxW37FSSQZ1JiwsST4cqQzDeyXtP79zkvFD3
1209843ms th_a thread.cpp:95 thread ] name:p2p tid:139731355076352
1209845ms th_a application.cpp:118 reset_p2p_node ] Configured p2p node to listen on 127.0.0.1:3939
Starting app2 and waiting 500 ms
1210345ms th_a application.cpp:190 operator() ] Initializing database...
1210345ms th_a application.cpp:63 create_example_genes ] Allocating all stake to 5KQwrPbwdL6PhXujxW37FSSQZ1JiwsST4cqQzDeyXtP79zkvFD3
1210349ms th_a thread.cpp:95 thread ] name:p2p tid:139731255420672
1210350ms th_a application.cpp:107 reset_p2p_node ] Adding seed node 127.0.0.1:3939
1210351ms th_a application.cpp:118 reset_p2p_node ] Configured p2p node to listen on 127.0.0.1:4040
/home/cc/graphene/src/graphene/tests/app/main.cpp(74): fatal error in "two_node_network": critical check app1.p2p_node()->get_connection_count() == 1 failed [0 != 1]
1210852ms th_a thread.cpp:115 ~thread ] calling quit() on p2p
1210852ms th_a thread.cpp:160 quit ] destroying boost thread 139731255420672
1210890ms th_a thread.cpp:115 ~thread ] calling quit() on p2p
1210890ms th_a thread.cpp:160 quit ] destroying boost thread 139731355076352
1210890ms p2p thread.cpp:246 exec ] thread canceled: 9 canceled_exception: Canceled
cancellation reason: [none given]
{"reason":"[none given]"}
p2p thread_d.hpp:463 start_next_fiber
*** 1 failure detected in test suite "Test Application"
```
This does not happen on every run, but usually shows up after several runs, if you don't see it after ~10 runs then I would assume your environment is unable to reproduce it.
A similar bug in the past was #55
_Copied from original issue: cryptonomex/graphene#159_ | 1.0 | Intermittent connection failure in app_test - _From @theoreticalbts on July 14, 2015 22:24_
After fixing generally obsolete `app_test` in cfd9dd0f75270f01c4d28b717e9117b732b63801 I notice that every few runs, I get the following error:
```
$ sudo -u graphene -H tests/app_test --log_level=message
Running 1 test case...
Creating temporary files
Creating and initializing app1
Creating and initializing app2
Starting app1 and waiting 500 ms
1209829ms th_a application.cpp:190 operator() ] Initializing database...
1209838ms th_a application.cpp:63 create_example_genes ] Allocating all stake to 5KQwrPbwdL6PhXujxW37FSSQZ1JiwsST4cqQzDeyXtP79zkvFD3
1209843ms th_a thread.cpp:95 thread ] name:p2p tid:139731355076352
1209845ms th_a application.cpp:118 reset_p2p_node ] Configured p2p node to listen on 127.0.0.1:3939
Starting app2 and waiting 500 ms
1210345ms th_a application.cpp:190 operator() ] Initializing database...
1210345ms th_a application.cpp:63 create_example_genes ] Allocating all stake to 5KQwrPbwdL6PhXujxW37FSSQZ1JiwsST4cqQzDeyXtP79zkvFD3
1210349ms th_a thread.cpp:95 thread ] name:p2p tid:139731255420672
1210350ms th_a application.cpp:107 reset_p2p_node ] Adding seed node 127.0.0.1:3939
1210351ms th_a application.cpp:118 reset_p2p_node ] Configured p2p node to listen on 127.0.0.1:4040
/home/cc/graphene/src/graphene/tests/app/main.cpp(74): fatal error in "two_node_network": critical check app1.p2p_node()->get_connection_count() == 1 failed [0 != 1]
1210852ms th_a thread.cpp:115 ~thread ] calling quit() on p2p
1210852ms th_a thread.cpp:160 quit ] destroying boost thread 139731255420672
1210890ms th_a thread.cpp:115 ~thread ] calling quit() on p2p
1210890ms th_a thread.cpp:160 quit ] destroying boost thread 139731355076352
1210890ms p2p thread.cpp:246 exec ] thread canceled: 9 canceled_exception: Canceled
cancellation reason: [none given]
{"reason":"[none given]"}
p2p thread_d.hpp:463 start_next_fiber
*** 1 failure detected in test suite "Test Application"
```
This does not happen on every run, but usually shows up after several runs, if you don't see it after ~10 runs then I would assume your environment is unable to reproduce it.
A similar bug in the past was #55
_Copied from original issue: cryptonomex/graphene#159_ | non_priority | intermittent connection failure in app test from theoreticalbts on july after fixing generally obsolete app test in i notice that every few runs i get the following error sudo u graphene h tests app test log level message running test case creating temporary files creating and initializing creating and initializing starting and waiting ms th a application cpp operator initializing database th a application cpp create example genes allocating all stake to th a thread cpp thread name tid th a application cpp reset node configured node to listen on starting and waiting ms th a application cpp operator initializing database th a application cpp create example genes allocating all stake to th a thread cpp thread name tid th a application cpp reset node adding seed node th a application cpp reset node configured node to listen on home cc graphene src graphene tests app main cpp fatal error in two node network critical check node get connection count failed th a thread cpp thread calling quit on th a thread cpp quit destroying boost thread th a thread cpp thread calling quit on th a thread cpp quit destroying boost thread thread cpp exec thread canceled canceled exception canceled cancellation reason reason thread d hpp start next fiber failure detected in test suite test application this does not happen on every run but usually shows up after several runs if you don t see it after runs then i would assume your environment is unable to reproduce it a similar bug in the past was copied from original issue cryptonomex graphene | 0 |
14,469 | 3,845,967,156 | IssuesEvent | 2016-04-05 01:07:44 | SOEN341-W16/ConUScheduler | https://api.github.com/repos/SOEN341-W16/ConUScheduler | closed | Deliverable 3 - 3.2.4 Security testing | documentation | NOTE: from what I reviewed, Cobalt did not have this part in their testing, check STAR's past project for this one
Your project should be tested for security, Including resistance to SQL injection attacks, against at least two automated tools (e.g Nikko and Skipfish).
| 1.0 | Deliverable 3 - 3.2.4 Security testing - NOTE: from what I reviewed, Cobalt did not have this part in their testing, check STAR's past project for this one
Your project should be tested for security, Including resistance to SQL injection attacks, against at least two automated tools (e.g Nikko and Skipfish).
| non_priority | deliverable security testing note from what i reviewed cobalt did not have this part in their testing check star s past project for this one your project should be tested for security including resistance to sql injection attacks against at least two automated tools e g nikko and skipfish | 0 |
3,238 | 5,399,379,099 | IssuesEvent | 2017-02-27 19:18:28 | Microsoft/vscode-cpptools | https://api.github.com/repos/Microsoft/vscode-cpptools | closed | Parameter Hints Doesn't Work Sometimes | Language Service | For example:
<img width="320" alt="2016-12-12 9 28 12" src="https://cloud.githubusercontent.com/assets/18381153/21085457/6117e13c-c04d-11e6-909e-869abbdc02cc.png">
I included "stdio.h"(already set the includePath), and type the function "printf", but Parameter Hints doesn't work. | 1.0 | Parameter Hints Doesn't Work Sometimes - For example:
<img width="320" alt="2016-12-12 9 28 12" src="https://cloud.githubusercontent.com/assets/18381153/21085457/6117e13c-c04d-11e6-909e-869abbdc02cc.png">
I included "stdio.h"(already set the includePath), and type the function "printf", but Parameter Hints doesn't work. | non_priority | parameter hints doesn t work sometimes for example img width alt src i included stdio h already set the includepath and type the function printf but parameter hints doesn t work | 0 |
184,012 | 14,267,186,108 | IssuesEvent | 2020-11-20 20:01:14 | AlaskaAirlines/WC-Generator | https://api.github.com/repos/AlaskaAirlines/WC-Generator | closed | generator: one demo page | Type: Feature Type: Testing | ## Is your feature request related to a problem? Please describe.
When building a new CE there is double work for documentation. Once in the dev env and then in the doc site.
## Describe the solution you'd like
What I would like to see is a single demo resource. E.g. a developer can update the demo page INSIDE the CE repo and this page is used to populate the CE page on the doc site.
This work could also include using the idea of the [Auro Demo Widget](https://github.com/AlaskaAirlines/auro/issues/198)
## Describe alternatives you've considered
The creation of the demo page in the doc site should be templated. Another thing to consider is that we can make CEs for the demo page so that we eat our own dog food and repurpose templates, not recreate UIs.
In addition to this, what about creating the demo page using Markdown? This would make the creation of the demo page easier, repeatable and there is no dependency on frameworks like React to generate the page. For the doc site there just needs to be a way to convert markdown to HTML.
| 1.0 | generator: one demo page - ## Is your feature request related to a problem? Please describe.
When building a new CE there is double work for documentation. Once in the dev env and then in the doc site.
## Describe the solution you'd like
What I would like to see is a single demo resource. E.g. a developer can update the demo page INSIDE the CE repo and this page is used to populate the CE page on the doc site.
This work could also include using the idea of the [Auro Demo Widget](https://github.com/AlaskaAirlines/auro/issues/198)
## Describe alternatives you've considered
The creation of the demo page in the doc site should be templated. Another thing to consider is that we can make CEs for the demo page so that we eat our own dog food and repurpose templates, not recreate UIs.
In addition to this, what about creating the demo page using Markdown? This would make the creation of the demo page easier, repeatable and there is no dependency on frameworks like React to generate the page. For the doc site there just needs to be a way to convert markdown to HTML.
| non_priority | generator one demo page is your feature request related to a problem please describe when building a new ce there is double work for documentation once in the dev env and then in the doc site describe the solution you d like what i would like to see is a single demo resource e g a developer can update the demo page inside the ce repo and this page is used to populate the ce page on the doc site this work could also include using the idea of the describe alternatives you ve considered the creation of the demo page in the doc site should be templated another thing to consider is that we can make ces for the demo page so that we eat our own dog food and repurpose templates not recreate uis in addition to this what about creating the demo page using markdown this would make the creation of the demo page easier repeatable and there is no dependency on frameworks like react to generate the page for the doc site there just needs to be a way to convert markdown to html | 0 |
235,006 | 25,901,410,716 | IssuesEvent | 2022-12-15 06:11:59 | Trinadh465/linux-3.0.35_CVE-2019-10220 | https://api.github.com/repos/Trinadh465/linux-3.0.35_CVE-2019-10220 | opened | CVE-2014-0155 (Medium) detected in linuxlinux-3.0.40 | security vulnerability | ## CVE-2014-0155 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-3.0.40</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v3.0/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v3.0/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/linux-3.0.35_CVE-2019-10220/commit/1ad216eff9de6bc4364330a52955ad1743ba56e2">1ad216eff9de6bc4364330a52955ad1743ba56e2</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/virt/kvm/ioapic.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/virt/kvm/ioapic.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/virt/kvm/ioapic.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The ioapic_deliver function in virt/kvm/ioapic.c in the Linux kernel through 3.14.1 does not properly validate the kvm_irq_delivery_to_apic return value, which allows guest OS users to cause a denial of service (host OS crash) via a crafted entry in the redirection table of an I/O APIC. NOTE: the affected code was moved to the ioapic_service function before the vulnerability was announced.
<p>Publish Date: 2014-04-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2014-0155>CVE-2014-0155</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2014-0155">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2014-0155</a></p>
<p>Release Date: 2014-04-14</p>
<p>Fix Resolution: v3.15-rc2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2014-0155 (Medium) detected in linuxlinux-3.0.40 - ## CVE-2014-0155 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-3.0.40</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v3.0/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v3.0/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/linux-3.0.35_CVE-2019-10220/commit/1ad216eff9de6bc4364330a52955ad1743ba56e2">1ad216eff9de6bc4364330a52955ad1743ba56e2</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/virt/kvm/ioapic.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/virt/kvm/ioapic.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/virt/kvm/ioapic.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The ioapic_deliver function in virt/kvm/ioapic.c in the Linux kernel through 3.14.1 does not properly validate the kvm_irq_delivery_to_apic return value, which allows guest OS users to cause a denial of service (host OS crash) via a crafted entry in the redirection table of an I/O APIC. NOTE: the affected code was moved to the ioapic_service function before the vulnerability was announced.
<p>Publish Date: 2014-04-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2014-0155>CVE-2014-0155</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2014-0155">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2014-0155</a></p>
<p>Release Date: 2014-04-14</p>
<p>Fix Resolution: v3.15-rc2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linuxlinux cve medium severity vulnerability vulnerable library linuxlinux apache software foundation asf library home page a href found in head commit a href found in base branch master vulnerable source files virt kvm ioapic c virt kvm ioapic c virt kvm ioapic c vulnerability details the ioapic deliver function in virt kvm ioapic c in the linux kernel through does not properly validate the kvm irq delivery to apic return value which allows guest os users to cause a denial of service host os crash via a crafted entry in the redirection table of an i o apic note the affected code was moved to the ioapic service function before the vulnerability was announced publish date url a href cvss score details base score metrics exploitability metrics attack vector adjacent attack complexity low privileges required low user interaction none scope changed impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
66,755 | 8,967,346,621 | IssuesEvent | 2019-01-29 02:56:18 | SAP/fundamental-react | https://api.github.com/repos/SAP/fundamental-react | opened | Add examples of importing components from the dist/ directory to docs | documentation enhancement | ### Description
After doing some research on tree shaking, I think the best way forward is to provide examples of how to import individual components from the `dist` folder if consumers want to reduce their library size.
ex:
```javascript
import {Alert} from 'react-fundamentals/dist/Alert/Alert'
```
### Versions
**fundamental-react:**
---
_**NOTE:** Where applicable, please include uncropped screen captures._
_**DISCLAIMER:**
After triaging an issue, the fundamental-react team will see if it can be reproduced or confirmed. If more information is needed, the fundamental-react team will contact the author. Any issues awaiting responses from the author for more than 7 days will be closed. The author can re-open the issue at a later time if they can present the requested information._ | 1.0 | Add examples of importing components from the dist/ directory to docs - ### Description
After doing some research on tree shaking, I think the best way forward is to provide examples of how to import individual components from the `dist` folder if consumers want to reduce their library size.
ex:
```javascript
import {Alert} from 'react-fundamentals/dist/Alert/Alert'
```
### Versions
**fundamental-react:**
---
_**NOTE:** Where applicable, please include uncropped screen captures._
_**DISCLAIMER:**
After triaging an issue, the fundamental-react team will see if it can be reproduced or confirmed. If more information is needed, the fundamental-react team will contact the author. Any issues awaiting responses from the author for more than 7 days will be closed. The author can re-open the issue at a later time if they can present the requested information._ | non_priority | add examples of importing components from the dist directory to docs description after doing some research on tree shaking i think the best way forward is to provide examples of how to import individual components from the dist folder if consumers want to reduce their library size ex javascript import alert from react fundamentals dist alert alert versions fundamental react note where applicable please include uncropped screen captures disclaimer after triaging an issue the fundamental react team will see if it can be reproduced or confirmed if more information is needed the fundamental react team will contact the author any issues awaiting responses from the author for more than days will be closed the author can re open the issue at a later time if they can present the requested information | 0 |
152,621 | 13,462,495,179 | IssuesEvent | 2020-09-09 16:09:04 | microsoft/FluidFramework | https://api.github.com/repos/microsoft/FluidFramework | opened | Add script to download and unzip api docs | documentation | While we don't want to force everyone to download the API docs, we should make them easier to install if they're trying to build the entire docs site.
We need to add a script to the /docs/package.json to download https://fluidframework.blob.core.windows.net/api-extractor-json/latest.tar.gz and then unzip it to the /docs/_api-extractor-temp folder.
Then update /docs/README.md to include those instructions | 1.0 | Add script to download and unzip api docs - While we don't want to force everyone to download the API docs, we should make them easier to install if they're trying to build the entire docs site.
We need to add a script to the /docs/package.json to download https://fluidframework.blob.core.windows.net/api-extractor-json/latest.tar.gz and then unzip it to the /docs/_api-extractor-temp folder.
Then update /docs/README.md to include those instructions | non_priority | add script to download and unzip api docs while we don t want to force everyone to download the api docs we should make them easier to install if they re trying to build the entire docs site we need to add a script to the docs package json to download and then unzip it to the docs api extractor temp folder then update docs readme md to include those instructions | 0 |
767 | 2,869,690,180 | IssuesEvent | 2015-06-06 12:42:57 | MISP/MISP | https://api.github.com/repos/MISP/MISP | closed | Is MISP affected by CVE-2015-4335 ? | potential-bug Security | Ubuntu 14 and RHEL 7 seem to include a vulnerable redis version without patches currently available. Does MISP use redis in a way that CVE-2015-4335 could be exploited? | True | Is MISP affected by CVE-2015-4335 ? - Ubuntu 14 and RHEL 7 seem to include a vulnerable redis version without patches currently available. Does MISP use redis in a way that CVE-2015-4335 could be exploited? | non_priority | is misp affected by cve ubuntu and rhel seem to include a vulnerable redis version without patches currently available does misp use redis in a way that cve could be exploited | 0 |
167,063 | 20,725,747,606 | IssuesEvent | 2022-03-14 01:29:30 | ghc-dev/Joshua-Contreras | https://api.github.com/repos/ghc-dev/Joshua-Contreras | opened | log4j-core-2.8.2.jar: 3 vulnerabilities (highest severity is: 10.0) | security vulnerability origin-Catherine-Reed | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-core-2.8.2.jar</b></p></summary>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/log4j-core/">https://logging.apache.org/log4j/2.x/log4j-core/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /sitory/org/apache/logging/log4j/log4j-core/2.8.2/log4j-core-2.8.2.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Catherine-Reed/commit/3470cd40d96ab8d244479801f2f1cd4e1ca2c721">3470cd40d96ab8d244479801f2f1cd4e1ca2c721</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-44228](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44228) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 10.0 | log4j-core-2.8.2.jar | Direct | org.apache.logging.log4j:log4j-core:2.15.0;org.ops4j.pax.logging:pax-logging-log4j2:1.11.10,2.0.11 | ❌ |
| [CVE-2021-45046](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-45046) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.0 | log4j-core-2.8.2.jar | Direct | org.apache.logging.log4j:log4j-core:2.12.2,2.16.0;org.ops4j.pax.logging:pax-logging-log4j2:1.11.11,2.0.12 | ❌ |
| [CVE-2020-9488](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9488) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | log4j-core-2.8.2.jar | Direct | org.apache.logging.log4j:log4j-core:2.13.2 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-44228</summary>
### Vulnerable Library - <b>log4j-core-2.8.2.jar</b></p>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/log4j-core/">https://logging.apache.org/log4j/2.x/log4j-core/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /sitory/org/apache/logging/log4j/log4j-core/2.8.2/log4j-core-2.8.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **log4j-core-2.8.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Catherine-Reed/commit/3470cd40d96ab8d244479801f2f1cd4e1ca2c721">3470cd40d96ab8d244479801f2f1cd4e1ca2c721</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Log4j2 2.0-beta9 through 2.15.0 (excluding security releases 2.12.2, 2.12.3, and 2.3.1) JNDI features used in configuration, log messages, and parameters do not protect against attacker controlled LDAP and other JNDI related endpoints. An attacker who can control log messages or log message parameters can execute arbitrary code loaded from LDAP servers when message lookup substitution is enabled. From log4j 2.15.0, this behavior has been disabled by default. From version 2.16.0 (along with 2.12.2, 2.12.3, and 2.3.1), this functionality has been completely removed. Note that this vulnerability is specific to log4j-core and does not affect log4net, log4cxx, or other Apache Logging Services projects.
<p>Publish Date: 2021-12-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44228>CVE-2021-44228</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>10.0</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://logging.apache.org/log4j/2.x/security.html">https://logging.apache.org/log4j/2.x/security.html</a></p>
<p>Release Date: 2021-12-10</p>
<p>Fix Resolution: org.apache.logging.log4j:log4j-core:2.15.0;org.ops4j.pax.logging:pax-logging-log4j2:1.11.10,2.0.11</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-45046</summary>
### Vulnerable Library - <b>log4j-core-2.8.2.jar</b></p>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/log4j-core/">https://logging.apache.org/log4j/2.x/log4j-core/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /sitory/org/apache/logging/log4j/log4j-core/2.8.2/log4j-core-2.8.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **log4j-core-2.8.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Catherine-Reed/commit/3470cd40d96ab8d244479801f2f1cd4e1ca2c721">3470cd40d96ab8d244479801f2f1cd4e1ca2c721</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
It was found that the fix to address CVE-2021-44228 in Apache Log4j 2.15.0 was incomplete in certain non-default configurations. This could allows attackers with control over Thread Context Map (MDC) input data when the logging configuration uses a non-default Pattern Layout with either a Context Lookup (for example, $${ctx:loginId}) or a Thread Context Map pattern (%X, %mdc, or %MDC) to craft malicious input data using a JNDI Lookup pattern resulting in an information leak and remote code execution in some environments and local code execution in all environments. Log4j 2.16.0 (Java 8) and 2.12.2 (Java 7) fix this issue by removing support for message lookup patterns and disabling JNDI functionality by default.
<p>Publish Date: 2021-12-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-45046>CVE-2021-45046</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.0</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://logging.apache.org/log4j/2.x/security.html">https://logging.apache.org/log4j/2.x/security.html</a></p>
<p>Release Date: 2021-12-14</p>
<p>Fix Resolution: org.apache.logging.log4j:log4j-core:2.12.2,2.16.0;org.ops4j.pax.logging:pax-logging-log4j2:1.11.11,2.0.12</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> CVE-2020-9488</summary>
### Vulnerable Library - <b>log4j-core-2.8.2.jar</b></p>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/log4j-core/">https://logging.apache.org/log4j/2.x/log4j-core/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /sitory/org/apache/logging/log4j/log4j-core/2.8.2/log4j-core-2.8.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **log4j-core-2.8.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Catherine-Reed/commit/3470cd40d96ab8d244479801f2f1cd4e1ca2c721">3470cd40d96ab8d244479801f2f1cd4e1ca2c721</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Improper validation of certificate with host mismatch in Apache Log4j SMTP appender. This could allow an SMTPS connection to be intercepted by a man-in-the-middle attack which could leak any log messages sent through that appender.
<p>Publish Date: 2020-04-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9488>CVE-2020-9488</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>3.7</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://issues.apache.org/jira/browse/LOG4J2-2819">https://issues.apache.org/jira/browse/LOG4J2-2819</a></p>
<p>Release Date: 2020-04-27</p>
<p>Fix Resolution: org.apache.logging.log4j:log4j-core:2.13.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.logging.log4j","packageName":"log4j-core","packageVersion":"2.8.2","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.apache.logging.log4j:log4j-core:2.8.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.logging.log4j:log4j-core:2.15.0;org.ops4j.pax.logging:pax-logging-log4j2:1.11.10,2.0.11","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-44228","vulnerabilityDetails":"Apache Log4j2 2.0-beta9 through 2.15.0 (excluding security releases 2.12.2, 2.12.3, and 2.3.1) JNDI features used in configuration, log messages, and parameters do not protect against attacker controlled LDAP and other JNDI related endpoints. An attacker who can control log messages or log message parameters can execute arbitrary code loaded from LDAP servers when message lookup substitution is enabled. From log4j 2.15.0, this behavior has been disabled by default. From version 2.16.0 (along with 2.12.2, 2.12.3, and 2.3.1), this functionality has been completely removed. Note that this vulnerability is specific to log4j-core and does not affect log4net, log4cxx, or other Apache Logging Services projects.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44228","cvss3Severity":"high","cvss3Score":"10.0","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.logging.log4j","packageName":"log4j-core","packageVersion":"2.8.2","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.apache.logging.log4j:log4j-core:2.8.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.logging.log4j:log4j-core:2.12.2,2.16.0;org.ops4j.pax.logging:pax-logging-log4j2:1.11.11,2.0.12","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-45046","vulnerabilityDetails":"It was found that the fix to address CVE-2021-44228 in Apache Log4j 2.15.0 was incomplete in certain non-default configurations. This could allows attackers with control over Thread Context Map (MDC) input data when the logging configuration uses a non-default Pattern Layout with either a Context Lookup (for example, $${ctx:loginId}) or a Thread Context Map pattern (%X, %mdc, or %MDC) to craft malicious input data using a JNDI Lookup pattern resulting in an information leak and remote code execution in some environments and local code execution in all environments. Log4j 2.16.0 (Java 8) and 2.12.2 (Java 7) fix this issue by removing support for message lookup patterns and disabling JNDI functionality by default.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-45046","cvss3Severity":"high","cvss3Score":"9.0","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.logging.log4j","packageName":"log4j-core","packageVersion":"2.8.2","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.apache.logging.log4j:log4j-core:2.8.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.logging.log4j:log4j-core:2.13.2","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-9488","vulnerabilityDetails":"Improper validation of certificate with host mismatch in Apache Log4j SMTP appender. This could allow an SMTPS connection to be intercepted by a man-in-the-middle attack which could leak any log messages sent through that appender.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9488","cvss3Severity":"low","cvss3Score":"3.7","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"None"},"extraData":{}}]</REMEDIATE> --> | True | log4j-core-2.8.2.jar: 3 vulnerabilities (highest severity is: 10.0) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-core-2.8.2.jar</b></p></summary>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/log4j-core/">https://logging.apache.org/log4j/2.x/log4j-core/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /sitory/org/apache/logging/log4j/log4j-core/2.8.2/log4j-core-2.8.2.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Catherine-Reed/commit/3470cd40d96ab8d244479801f2f1cd4e1ca2c721">3470cd40d96ab8d244479801f2f1cd4e1ca2c721</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-44228](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44228) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 10.0 | log4j-core-2.8.2.jar | Direct | org.apache.logging.log4j:log4j-core:2.15.0;org.ops4j.pax.logging:pax-logging-log4j2:1.11.10,2.0.11 | ❌ |
| [CVE-2021-45046](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-45046) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.0 | log4j-core-2.8.2.jar | Direct | org.apache.logging.log4j:log4j-core:2.12.2,2.16.0;org.ops4j.pax.logging:pax-logging-log4j2:1.11.11,2.0.12 | ❌ |
| [CVE-2020-9488](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9488) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | log4j-core-2.8.2.jar | Direct | org.apache.logging.log4j:log4j-core:2.13.2 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-44228</summary>
### Vulnerable Library - <b>log4j-core-2.8.2.jar</b></p>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/log4j-core/">https://logging.apache.org/log4j/2.x/log4j-core/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /sitory/org/apache/logging/log4j/log4j-core/2.8.2/log4j-core-2.8.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **log4j-core-2.8.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Catherine-Reed/commit/3470cd40d96ab8d244479801f2f1cd4e1ca2c721">3470cd40d96ab8d244479801f2f1cd4e1ca2c721</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Log4j2 2.0-beta9 through 2.15.0 (excluding security releases 2.12.2, 2.12.3, and 2.3.1) JNDI features used in configuration, log messages, and parameters do not protect against attacker controlled LDAP and other JNDI related endpoints. An attacker who can control log messages or log message parameters can execute arbitrary code loaded from LDAP servers when message lookup substitution is enabled. From log4j 2.15.0, this behavior has been disabled by default. From version 2.16.0 (along with 2.12.2, 2.12.3, and 2.3.1), this functionality has been completely removed. Note that this vulnerability is specific to log4j-core and does not affect log4net, log4cxx, or other Apache Logging Services projects.
<p>Publish Date: 2021-12-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44228>CVE-2021-44228</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>10.0</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://logging.apache.org/log4j/2.x/security.html">https://logging.apache.org/log4j/2.x/security.html</a></p>
<p>Release Date: 2021-12-10</p>
<p>Fix Resolution: org.apache.logging.log4j:log4j-core:2.15.0;org.ops4j.pax.logging:pax-logging-log4j2:1.11.10,2.0.11</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-45046</summary>
### Vulnerable Library - <b>log4j-core-2.8.2.jar</b></p>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/log4j-core/">https://logging.apache.org/log4j/2.x/log4j-core/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /sitory/org/apache/logging/log4j/log4j-core/2.8.2/log4j-core-2.8.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **log4j-core-2.8.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Catherine-Reed/commit/3470cd40d96ab8d244479801f2f1cd4e1ca2c721">3470cd40d96ab8d244479801f2f1cd4e1ca2c721</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
It was found that the fix to address CVE-2021-44228 in Apache Log4j 2.15.0 was incomplete in certain non-default configurations. This could allows attackers with control over Thread Context Map (MDC) input data when the logging configuration uses a non-default Pattern Layout with either a Context Lookup (for example, $${ctx:loginId}) or a Thread Context Map pattern (%X, %mdc, or %MDC) to craft malicious input data using a JNDI Lookup pattern resulting in an information leak and remote code execution in some environments and local code execution in all environments. Log4j 2.16.0 (Java 8) and 2.12.2 (Java 7) fix this issue by removing support for message lookup patterns and disabling JNDI functionality by default.
<p>Publish Date: 2021-12-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-45046>CVE-2021-45046</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.0</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://logging.apache.org/log4j/2.x/security.html">https://logging.apache.org/log4j/2.x/security.html</a></p>
<p>Release Date: 2021-12-14</p>
<p>Fix Resolution: org.apache.logging.log4j:log4j-core:2.12.2,2.16.0;org.ops4j.pax.logging:pax-logging-log4j2:1.11.11,2.0.12</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> CVE-2020-9488</summary>
### Vulnerable Library - <b>log4j-core-2.8.2.jar</b></p>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/log4j-core/">https://logging.apache.org/log4j/2.x/log4j-core/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /sitory/org/apache/logging/log4j/log4j-core/2.8.2/log4j-core-2.8.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **log4j-core-2.8.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Catherine-Reed/commit/3470cd40d96ab8d244479801f2f1cd4e1ca2c721">3470cd40d96ab8d244479801f2f1cd4e1ca2c721</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Improper validation of certificate with host mismatch in Apache Log4j SMTP appender. This could allow an SMTPS connection to be intercepted by a man-in-the-middle attack which could leak any log messages sent through that appender.
<p>Publish Date: 2020-04-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9488>CVE-2020-9488</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>3.7</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://issues.apache.org/jira/browse/LOG4J2-2819">https://issues.apache.org/jira/browse/LOG4J2-2819</a></p>
<p>Release Date: 2020-04-27</p>
<p>Fix Resolution: org.apache.logging.log4j:log4j-core:2.13.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.logging.log4j","packageName":"log4j-core","packageVersion":"2.8.2","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.apache.logging.log4j:log4j-core:2.8.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.logging.log4j:log4j-core:2.15.0;org.ops4j.pax.logging:pax-logging-log4j2:1.11.10,2.0.11","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-44228","vulnerabilityDetails":"Apache Log4j2 2.0-beta9 through 2.15.0 (excluding security releases 2.12.2, 2.12.3, and 2.3.1) JNDI features used in configuration, log messages, and parameters do not protect against attacker controlled LDAP and other JNDI related endpoints. An attacker who can control log messages or log message parameters can execute arbitrary code loaded from LDAP servers when message lookup substitution is enabled. From log4j 2.15.0, this behavior has been disabled by default. From version 2.16.0 (along with 2.12.2, 2.12.3, and 2.3.1), this functionality has been completely removed. Note that this vulnerability is specific to log4j-core and does not affect log4net, log4cxx, or other Apache Logging Services projects.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44228","cvss3Severity":"high","cvss3Score":"10.0","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.logging.log4j","packageName":"log4j-core","packageVersion":"2.8.2","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.apache.logging.log4j:log4j-core:2.8.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.logging.log4j:log4j-core:2.12.2,2.16.0;org.ops4j.pax.logging:pax-logging-log4j2:1.11.11,2.0.12","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-45046","vulnerabilityDetails":"It was found that the fix to address CVE-2021-44228 in Apache Log4j 2.15.0 was incomplete in certain non-default configurations. This could allows attackers with control over Thread Context Map (MDC) input data when the logging configuration uses a non-default Pattern Layout with either a Context Lookup (for example, $${ctx:loginId}) or a Thread Context Map pattern (%X, %mdc, or %MDC) to craft malicious input data using a JNDI Lookup pattern resulting in an information leak and remote code execution in some environments and local code execution in all environments. Log4j 2.16.0 (Java 8) and 2.12.2 (Java 7) fix this issue by removing support for message lookup patterns and disabling JNDI functionality by default.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-45046","cvss3Severity":"high","cvss3Score":"9.0","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.logging.log4j","packageName":"log4j-core","packageVersion":"2.8.2","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.apache.logging.log4j:log4j-core:2.8.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.logging.log4j:log4j-core:2.13.2","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-9488","vulnerabilityDetails":"Improper validation of certificate with host mismatch in Apache Log4j SMTP appender. This could allow an SMTPS connection to be intercepted by a man-in-the-middle attack which could leak any log messages sent through that appender.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9488","cvss3Severity":"low","cvss3Score":"3.7","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"None"},"extraData":{}}]</REMEDIATE> --> | non_priority | core jar vulnerabilities highest severity is vulnerable library core jar the apache implementation library home page a href path to dependency file pom xml path to vulnerable library sitory org apache logging core core jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high core jar direct org apache logging core org pax logging pax logging high core jar direct org apache logging core org pax logging pax logging low core jar direct org apache logging core details cve vulnerable library core jar the apache implementation library home page a href path to dependency file pom xml path to vulnerable library sitory org apache logging core core jar dependency hierarchy x core jar vulnerable library found in head commit a href found in base branch main vulnerability details apache through excluding security releases and jndi features used in configuration log messages and parameters do not protect against attacker controlled ldap and other jndi related endpoints an attacker who can control log messages or log message parameters can execute arbitrary code loaded from ldap servers when message lookup substitution is enabled from this behavior has been disabled by default from version along with and this functionality has been completely removed note that this vulnerability is specific to core and does not affect or other apache logging services projects publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache logging core org pax logging pax logging cve vulnerable library core jar the apache implementation library home page a href path to dependency file pom xml path to vulnerable library sitory org apache logging core core jar dependency hierarchy x core jar vulnerable library found in head commit a href found in base branch main vulnerability details it was found that the fix to address cve in apache was incomplete in certain non default configurations this could allows attackers with control over thread context map mdc input data when the logging configuration uses a non default pattern layout with either a context lookup for example ctx loginid or a thread context map pattern x mdc or mdc to craft malicious input data using a jndi lookup pattern resulting in an information leak and remote code execution in some environments and local code execution in all environments java and java fix this issue by removing support for message lookup patterns and disabling jndi functionality by default publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache logging core org pax logging pax logging cve vulnerable library core jar the apache implementation library home page a href path to dependency file pom xml path to vulnerable library sitory org apache logging core core jar dependency hierarchy x core jar vulnerable library found in head commit a href found in base branch main vulnerability details improper validation of certificate with host mismatch in apache smtp appender this could allow an smtps connection to be intercepted by a man in the middle attack which could leak any log messages sent through that appender publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache logging core rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue istransitivedependency false dependencytree org apache logging core isminimumfixversionavailable true minimumfixversion org apache logging core org pax logging pax logging isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails apache through excluding security releases and jndi features used in configuration log messages and parameters do not protect against attacker controlled ldap and other jndi related endpoints an attacker who can control log messages or log message parameters can execute arbitrary code loaded from ldap servers when message lookup substitution is enabled from this behavior has been disabled by default from version along with and this functionality has been completely removed note that this vulnerability is specific to core and does not affect or other apache logging services projects vulnerabilityurl istransitivedependency false dependencytree org apache logging core isminimumfixversionavailable true minimumfixversion org apache logging core org pax logging pax logging isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails it was found that the fix to address cve in apache was incomplete in certain non default configurations this could allows attackers with control over thread context map mdc input data when the logging configuration uses a non default pattern layout with either a context lookup for example ctx loginid or a thread context map pattern x mdc or mdc to craft malicious input data using a jndi lookup pattern resulting in an information leak and remote code execution in some environments and local code execution in all environments java and java fix this issue by removing support for message lookup patterns and disabling jndi functionality by default vulnerabilityurl istransitivedependency false dependencytree org apache logging core isminimumfixversionavailable true minimumfixversion org apache logging core isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails improper validation of certificate with host mismatch in apache smtp appender this could allow an smtps connection to be intercepted by a man in the middle attack which could leak any log messages sent through that appender vulnerabilityurl | 0 |
196 | 2,658,764,785 | IssuesEvent | 2015-03-18 17:15:41 | mirage/mirage | https://api.github.com/repos/mirage/mirage | opened | Better error handling | breaks compatibility new feature | See http://lists.xenproject.org/archives/html/mirageos-devel/2015-01/msg00143.html
Tasks:
* [ ] add `val pp_error: Format.formatter -> error -> unit` in both `V1.FLOW` and `V1.DEVICE`
* [ ] fix `mirage-tcpip`
* [ ] ... | True | Better error handling - See http://lists.xenproject.org/archives/html/mirageos-devel/2015-01/msg00143.html
Tasks:
* [ ] add `val pp_error: Format.formatter -> error -> unit` in both `V1.FLOW` and `V1.DEVICE`
* [ ] fix `mirage-tcpip`
* [ ] ... | non_priority | better error handling see tasks add val pp error format formatter error unit in both flow and device fix mirage tcpip | 0 |
52,486 | 22,263,810,665 | IssuesEvent | 2022-06-10 04:52:43 | klubcoin/lcn-mobile | https://api.github.com/repos/klubcoin/lcn-mobile | opened | [Pay online service] Redirect to Klubcoin Dashboard Screen while cancel payment | Should Have PayOnline Services | ### **Description:**
- Redirect to Klubcoin Dashboard Screen while cancel payment
| 1.0 | [Pay online service] Redirect to Klubcoin Dashboard Screen while cancel payment - ### **Description:**
- Redirect to Klubcoin Dashboard Screen while cancel payment
| non_priority | redirect to klubcoin dashboard screen while cancel payment description redirect to klubcoin dashboard screen while cancel payment | 0 |
108,597 | 13,642,220,771 | IssuesEvent | 2020-09-25 15:13:31 | desktop/desktop | https://api.github.com/repos/desktop/desktop | closed | Mass select files from highlight | design-input-needed enhancement | ### Describe the feature or problem you’d like to solve
Highlight and select, I would like to highlight around 3000 files and select them out of 60,000 changes.
Currently I have not found a way to quickly select more then one file at a time. I can highlight them but not select them.
I'm trying to slowly commit a large project I was given and currently have not found an easy way to select a group of highlighted files. These are various files of numerous size so I do not want to commit the full 60k as it will timeout.
### Proposed solution
It will benefit everyone using this. Please allow me the ability to either select all highlighted with a button or let me right click and select them from a menu option. Currently all I see is a select all button, but I only want to select the highlighted files.
### Additional context
Add any other context like screenshots or mockups are helpful, if applicable.
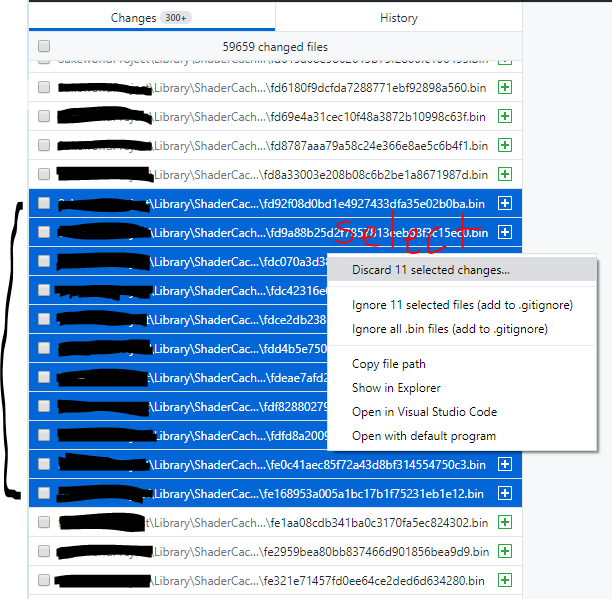
| 1.0 | Mass select files from highlight - ### Describe the feature or problem you’d like to solve
Highlight and select, I would like to highlight around 3000 files and select them out of 60,000 changes.
Currently I have not found a way to quickly select more then one file at a time. I can highlight them but not select them.
I'm trying to slowly commit a large project I was given and currently have not found an easy way to select a group of highlighted files. These are various files of numerous size so I do not want to commit the full 60k as it will timeout.
### Proposed solution
It will benefit everyone using this. Please allow me the ability to either select all highlighted with a button or let me right click and select them from a menu option. Currently all I see is a select all button, but I only want to select the highlighted files.
### Additional context
Add any other context like screenshots or mockups are helpful, if applicable.
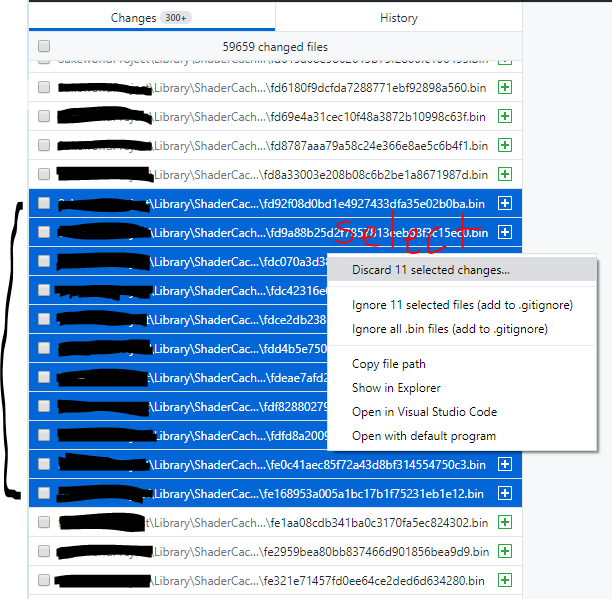
| non_priority | mass select files from highlight describe the feature or problem you’d like to solve highlight and select i would like to highlight around files and select them out of changes currently i have not found a way to quickly select more then one file at a time i can highlight them but not select them i m trying to slowly commit a large project i was given and currently have not found an easy way to select a group of highlighted files these are various files of numerous size so i do not want to commit the full as it will timeout proposed solution it will benefit everyone using this please allow me the ability to either select all highlighted with a button or let me right click and select them from a menu option currently all i see is a select all button but i only want to select the highlighted files additional context add any other context like screenshots or mockups are helpful if applicable | 0 |
401,634 | 27,333,957,424 | IssuesEvent | 2023-02-26 00:43:42 | gpauloski/kfac-pytorch | https://api.github.com/repos/gpauloski/kfac-pytorch | closed | Add Apex as optional requirement | documentation | ### Describe the Request
Apex is an optional dependency that should be noted in the readme. Maybe it should also be an optional dependency in `setup.cfg`? | 1.0 | Add Apex as optional requirement - ### Describe the Request
Apex is an optional dependency that should be noted in the readme. Maybe it should also be an optional dependency in `setup.cfg`? | non_priority | add apex as optional requirement describe the request apex is an optional dependency that should be noted in the readme maybe it should also be an optional dependency in setup cfg | 0 |
327,951 | 24,163,081,283 | IssuesEvent | 2022-09-22 13:10:59 | Engineering-Design-2022/snop-vs | https://api.github.com/repos/Engineering-Design-2022/snop-vs | closed | NumberOfPeopleBean.java - javadoc の記述 | documentation | # Overview <!-- where/what improvements you want to make -->
NumberOfPeopleBean.java の javadoc を記述する
# Background of the improvement <!-- background of the improvement needed -->
# Requirements <!-- expected behavior or content to be met -->
# Considerations <!-- Items that need to be considered for improvement -->
- #20 の内容を参考にする
# Implementation policy <!-- how to implement -->
-
# Test items <!-- how to check if the improvement has been implemented correctly -->
-
# Remarks <!-- any other comments -->
<!-- You don't have to fill in all the blanks, but write the necessary information clearly. --> | 1.0 | NumberOfPeopleBean.java - javadoc の記述 - # Overview <!-- where/what improvements you want to make -->
NumberOfPeopleBean.java の javadoc を記述する
# Background of the improvement <!-- background of the improvement needed -->
# Requirements <!-- expected behavior or content to be met -->
# Considerations <!-- Items that need to be considered for improvement -->
- #20 の内容を参考にする
# Implementation policy <!-- how to implement -->
-
# Test items <!-- how to check if the improvement has been implemented correctly -->
-
# Remarks <!-- any other comments -->
<!-- You don't have to fill in all the blanks, but write the necessary information clearly. --> | non_priority | numberofpeoplebean java javadoc の記述 overview numberofpeoplebean java の javadoc を記述する background of the improvement requirements considerations の内容を参考にする implementation policy test items remarks | 0 |
18,558 | 24,555,553,663 | IssuesEvent | 2022-10-12 15:36:05 | GoogleCloudPlatform/fda-mystudies | https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies | closed | [Android] [Offline indicator] Share button should be disabled in the below mentioned screens when participant is offline | Bug P1 Android Process: Fixed Process: Tested QA Process: Tested dev | Share button should be disabled in all the below mentioned screens when the participant is offline
1. App glossary
2. Dashboard
3. Consent pdf ( both resources screen and study overview screen)
| 3.0 | [Android] [Offline indicator] Share button should be disabled in the below mentioned screens when participant is offline - Share button should be disabled in all the below mentioned screens when the participant is offline
1. App glossary
2. Dashboard
3. Consent pdf ( both resources screen and study overview screen)
| non_priority | share button should be disabled in the below mentioned screens when participant is offline share button should be disabled in all the below mentioned screens when the participant is offline app glossary dashboard consent pdf both resources screen and study overview screen | 0 |
99,078 | 8,689,623,483 | IssuesEvent | 2018-12-03 19:13:32 | iotaledger/iri | https://api.github.com/repos/iotaledger/iri | closed | Test the LOCAL_SNAPSHOTS_BASE_PATH flag | E-Testing Local Snapshots | ### Description
General tests for the LOCAL_SNAPSHOTS_BASE_PATH flag.
1. That file is actually created under the PATH.
2. What happens if snapshot path is absent after restart.
3. Test different, non-default paths.
4. Test changing the path between node restarts. Node stops with one path, is started with a different one.
| 1.0 | Test the LOCAL_SNAPSHOTS_BASE_PATH flag - ### Description
General tests for the LOCAL_SNAPSHOTS_BASE_PATH flag.
1. That file is actually created under the PATH.
2. What happens if snapshot path is absent after restart.
3. Test different, non-default paths.
4. Test changing the path between node restarts. Node stops with one path, is started with a different one.
| non_priority | test the local snapshots base path flag description general tests for the local snapshots base path flag that file is actually created under the path what happens if snapshot path is absent after restart test different non default paths test changing the path between node restarts node stops with one path is started with a different one | 0 |
168,429 | 20,764,094,415 | IssuesEvent | 2022-03-15 18:54:55 | husnuljahneer/express-api | https://api.github.com/repos/husnuljahneer/express-api | opened | bcrypt-5.0.1.tgz: 1 vulnerabilities (highest severity is: 6.1) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcrypt-5.0.1.tgz</b></p></summary>
<p></p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/husnuljahneer/express-api/commit/654038fa58dd56d7138edd12ae73fed721ddf980">654038fa58dd56d7138edd12ae73fed721ddf980</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2022-0235](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0235) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | node-fetch-2.6.6.tgz | Transitive | N/A | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-0235</summary>
### Vulnerable Library - <b>node-fetch-2.6.6.tgz</b></p>
<p>A light-weight module that brings window.fetch to node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.6.tgz">https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.6.tgz</a></p>
<p>
Dependency Hierarchy:
- bcrypt-5.0.1.tgz (Root Library)
- node-pre-gyp-1.0.8.tgz
- :x: **node-fetch-2.6.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/husnuljahneer/express-api/commit/654038fa58dd56d7138edd12ae73fed721ddf980">654038fa58dd56d7138edd12ae73fed721ddf980</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
node-fetch is vulnerable to Exposure of Sensitive Information to an Unauthorized Actor
<p>Publish Date: 2022-01-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0235>CVE-2022-0235</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-r683-j2x4-v87g">https://github.com/advisories/GHSA-r683-j2x4-v87g</a></p>
<p>Release Date: 2022-01-16</p>
<p>Fix Resolution: node-fetch - 2.6.7,3.1.1</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-fetch","packageVersion":"2.6.6","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"bcrypt:5.0.1;@mapbox/node-pre-gyp:1.0.8;node-fetch:2.6.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"node-fetch - 2.6.7,3.1.1","isBinary":true}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-0235","vulnerabilityDetails":"node-fetch is vulnerable to Exposure of Sensitive Information to an Unauthorized Actor","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0235","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}]</REMEDIATE> --> | True | bcrypt-5.0.1.tgz: 1 vulnerabilities (highest severity is: 6.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcrypt-5.0.1.tgz</b></p></summary>
<p></p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/husnuljahneer/express-api/commit/654038fa58dd56d7138edd12ae73fed721ddf980">654038fa58dd56d7138edd12ae73fed721ddf980</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2022-0235](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0235) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | node-fetch-2.6.6.tgz | Transitive | N/A | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-0235</summary>
### Vulnerable Library - <b>node-fetch-2.6.6.tgz</b></p>
<p>A light-weight module that brings window.fetch to node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.6.tgz">https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.6.tgz</a></p>
<p>
Dependency Hierarchy:
- bcrypt-5.0.1.tgz (Root Library)
- node-pre-gyp-1.0.8.tgz
- :x: **node-fetch-2.6.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/husnuljahneer/express-api/commit/654038fa58dd56d7138edd12ae73fed721ddf980">654038fa58dd56d7138edd12ae73fed721ddf980</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
node-fetch is vulnerable to Exposure of Sensitive Information to an Unauthorized Actor
<p>Publish Date: 2022-01-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0235>CVE-2022-0235</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-r683-j2x4-v87g">https://github.com/advisories/GHSA-r683-j2x4-v87g</a></p>
<p>Release Date: 2022-01-16</p>
<p>Fix Resolution: node-fetch - 2.6.7,3.1.1</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-fetch","packageVersion":"2.6.6","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"bcrypt:5.0.1;@mapbox/node-pre-gyp:1.0.8;node-fetch:2.6.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"node-fetch - 2.6.7,3.1.1","isBinary":true}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-0235","vulnerabilityDetails":"node-fetch is vulnerable to Exposure of Sensitive Information to an Unauthorized Actor","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0235","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}]</REMEDIATE> --> | non_priority | bcrypt tgz vulnerabilities highest severity is vulnerable library bcrypt tgz found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available medium node fetch tgz transitive n a details cve vulnerable library node fetch tgz a light weight module that brings window fetch to node js library home page a href dependency hierarchy bcrypt tgz root library node pre gyp tgz x node fetch tgz vulnerable library found in head commit a href found in base branch master vulnerability details node fetch is vulnerable to exposure of sensitive information to an unauthorized actor publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution node fetch step up your open source security game with whitesource istransitivedependency true dependencytree bcrypt mapbox node pre gyp node fetch isminimumfixversionavailable true minimumfixversion node fetch isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails node fetch is vulnerable to exposure of sensitive information to an unauthorized actor vulnerabilityurl | 0 |
345,997 | 30,858,252,513 | IssuesEvent | 2023-08-02 23:01:54 | peternied/OpenSearch-1 | https://api.github.com/repos/peternied/OpenSearch-1 | closed | [AUTOCUT] Gradle Check Failure on push to limited-scopes | bug >test-failure autocut | Gradle check has failed on push of your commit 2f24adadb871de4e802e45755d469b53a3931270.
Please examine the workflow log .
Is the failure [a flaky test](https://github.com/opensearch-project/OpenSearch/blob/main/DEVELOPER_GUIDE.md#flaky-tests) unrelated to your change?
| 1.0 | [AUTOCUT] Gradle Check Failure on push to limited-scopes - Gradle check has failed on push of your commit 2f24adadb871de4e802e45755d469b53a3931270.
Please examine the workflow log .
Is the failure [a flaky test](https://github.com/opensearch-project/OpenSearch/blob/main/DEVELOPER_GUIDE.md#flaky-tests) unrelated to your change?
| non_priority | gradle check failure on push to limited scopes gradle check has failed on push of your commit please examine the workflow log is the failure unrelated to your change | 0 |
111,218 | 24,089,055,896 | IssuesEvent | 2022-09-19 13:26:05 | sourcegraph/sourcegraph | https://api.github.com/repos/sourcegraph/sourcegraph | opened | insights: add metric to track aggregation timeouts | team/code-insights backend insights-aggregation-4.X | Add an additional metric to aggregations that tracks if the request hits a timeout. This should be in addition to the current `mode` and `extendedTimeout` values that are captured. | 1.0 | insights: add metric to track aggregation timeouts - Add an additional metric to aggregations that tracks if the request hits a timeout. This should be in addition to the current `mode` and `extendedTimeout` values that are captured. | non_priority | insights add metric to track aggregation timeouts add an additional metric to aggregations that tracks if the request hits a timeout this should be in addition to the current mode and extendedtimeout values that are captured | 0 |
38,820 | 6,706,500,560 | IssuesEvent | 2017-10-12 07:21:15 | JetBrains/Exposed | https://api.github.com/repos/JetBrains/Exposed | closed | innerJoin table twice | documentation | In my project i have table with multiple keys refers same table, like this:
object Users : Table() {
val id = varchar(“id”, 10).primaryKey()
val name = varchar(“name”, length = 50)
val residentialCityId = (integer(“city_id”) references Cities.id).nullable()
val bornCityId = (integer(“city_id”) references Cities.id).nullable()
}
object Cities : Table() {
val id = integer(“id”).autoIncrement().primaryKey() // Column
val name = varchar(“name”, 50) // Column
}
so i have to join same table 2 times, i need something like this:
Users.join(Cities.alias(“ResidentialCiti”), JoinType.INNER, Users.residentialCityId, Cities.id)
.join(Cities.alias(“BornCiti”), JoinType.INNER, Users.bornCityId, Cities.id).slice(…).selectAll()
this one is wrong, and i cant understand how to do it…
There is also generic in Table.kt:
fun <C1:ColumnSet, C2:ColumnSet> C1.innerJoin(otherTable: C2, onColumn: C1.() -> Expression<>, otherColumn: C2.() -> Expression<>) = join(otherTable, JoinType.INNER, onColumn(this), otherColumn(otherTable))
can it be used for this case and how to use it in general? i dont understand how to set onColumn/otherColumn parameters
| 1.0 | innerJoin table twice - In my project i have table with multiple keys refers same table, like this:
object Users : Table() {
val id = varchar(“id”, 10).primaryKey()
val name = varchar(“name”, length = 50)
val residentialCityId = (integer(“city_id”) references Cities.id).nullable()
val bornCityId = (integer(“city_id”) references Cities.id).nullable()
}
object Cities : Table() {
val id = integer(“id”).autoIncrement().primaryKey() // Column
val name = varchar(“name”, 50) // Column
}
so i have to join same table 2 times, i need something like this:
Users.join(Cities.alias(“ResidentialCiti”), JoinType.INNER, Users.residentialCityId, Cities.id)
.join(Cities.alias(“BornCiti”), JoinType.INNER, Users.bornCityId, Cities.id).slice(…).selectAll()
this one is wrong, and i cant understand how to do it…
There is also generic in Table.kt:
fun <C1:ColumnSet, C2:ColumnSet> C1.innerJoin(otherTable: C2, onColumn: C1.() -> Expression<>, otherColumn: C2.() -> Expression<>) = join(otherTable, JoinType.INNER, onColumn(this), otherColumn(otherTable))
can it be used for this case and how to use it in general? i dont understand how to set onColumn/otherColumn parameters
| non_priority | innerjoin table twice in my project i have table with multiple keys refers same table like this object users table val id varchar “id” primarykey val name varchar “name” length val residentialcityid integer “city id” references cities id nullable val borncityid integer “city id” references cities id nullable object cities table val id integer “id” autoincrement primarykey column val name varchar “name” column so i have to join same table times i need something like this users join cities alias “residentialciti” jointype inner users residentialcityid cities id join cities alias “bornciti” jointype inner users borncityid cities id slice … selectall this one is wrong and i cant understand how to do it… there is also generic in table kt fun innerjoin othertable oncolumn expression othercolumn expression join othertable jointype inner oncolumn this othercolumn othertable can it be used for this case and how to use it in general i dont understand how to set oncolumn othercolumn parameters | 0 |
221,372 | 17,346,756,830 | IssuesEvent | 2021-07-29 00:41:18 | microsoft/AzureStorageExplorer | https://api.github.com/repos/microsoft/AzureStorageExplorer | closed | Keep consistent behaviors for the tag group query on the navigate bar and filter panel after clicking 'Reset' | :gear: blobs 🧪 testing | **Storage Explorer Version**: 1.21.0-dev
**Build Number**: 20210726.1
**Branch**: main
**Platform/OS**: Windows 10/ Linux Ubuntu 20.04/ MacOS Big Sur 11.4
**Architecture**: ia32/x64
**How Found**: Exploratory testing
**Regression From**: Not a regression
## Steps to Reproduce ##
1. Expand one Non-ADLS Gen2 storage account -> Blob Containers.
2. Select one blob container and open it -> Click 'Show View Options'.
3. Select 'Tag Query' -> Click 'Apply'.
4. Click 'Add Clause' -> Type a valid tagkey and tagvalue -> Click 'Apply'.
5. Click 'Add Clause' -> Type a valid tagkey and tagvalue -> Click 'Apply'.
7. Click 'Reset' -> Observe the navigation bar and the filter panel.
9. Check whether the behaviors are consistent.
## Expected Experience ##
The behaviors are inconsistent.
## Actual Experience ##
The behaviors are consistent.
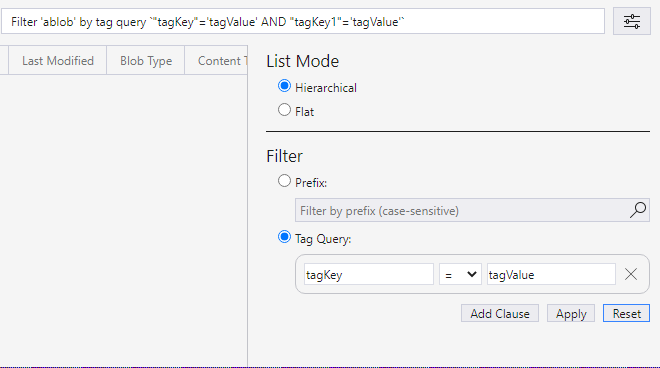
| 1.0 | Keep consistent behaviors for the tag group query on the navigate bar and filter panel after clicking 'Reset' - **Storage Explorer Version**: 1.21.0-dev
**Build Number**: 20210726.1
**Branch**: main
**Platform/OS**: Windows 10/ Linux Ubuntu 20.04/ MacOS Big Sur 11.4
**Architecture**: ia32/x64
**How Found**: Exploratory testing
**Regression From**: Not a regression
## Steps to Reproduce ##
1. Expand one Non-ADLS Gen2 storage account -> Blob Containers.
2. Select one blob container and open it -> Click 'Show View Options'.
3. Select 'Tag Query' -> Click 'Apply'.
4. Click 'Add Clause' -> Type a valid tagkey and tagvalue -> Click 'Apply'.
5. Click 'Add Clause' -> Type a valid tagkey and tagvalue -> Click 'Apply'.
7. Click 'Reset' -> Observe the navigation bar and the filter panel.
9. Check whether the behaviors are consistent.
## Expected Experience ##
The behaviors are inconsistent.
## Actual Experience ##
The behaviors are consistent.
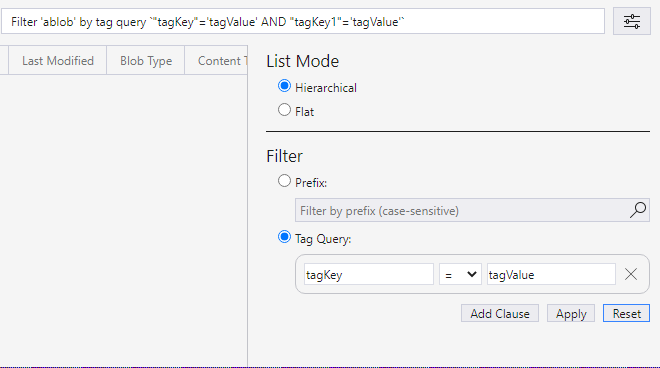
| non_priority | keep consistent behaviors for the tag group query on the navigate bar and filter panel after clicking reset storage explorer version dev build number branch main platform os windows linux ubuntu macos big sur architecture how found exploratory testing regression from not a regression steps to reproduce expand one non adls storage account blob containers select one blob container and open it click show view options select tag query click apply click add clause type a valid tagkey and tagvalue click apply click add clause type a valid tagkey and tagvalue click apply click reset observe the navigation bar and the filter panel check whether the behaviors are consistent expected experience the behaviors are inconsistent actual experience the behaviors are consistent | 0 |
74,425 | 14,248,685,783 | IssuesEvent | 2020-11-19 13:17:32 | electrumsv/electrumsv-sdk | https://api.github.com/repos/electrumsv/electrumsv-sdk | closed | global_cli_flags can currently mutate globally which makes the code more complex than it should be | code quality | I'd like to assign the global_cli_flags to a named tuple as early as possible in the pipeline and pass it into each function call (namely the main plugin entrypoints)... which will alleviate any worries about mutating global state and causing bugs...
Given use of recursion, it feels like bugs are just waiting to happen due to this.. | 1.0 | global_cli_flags can currently mutate globally which makes the code more complex than it should be - I'd like to assign the global_cli_flags to a named tuple as early as possible in the pipeline and pass it into each function call (namely the main plugin entrypoints)... which will alleviate any worries about mutating global state and causing bugs...
Given use of recursion, it feels like bugs are just waiting to happen due to this.. | non_priority | global cli flags can currently mutate globally which makes the code more complex than it should be i d like to assign the global cli flags to a named tuple as early as possible in the pipeline and pass it into each function call namely the main plugin entrypoints which will alleviate any worries about mutating global state and causing bugs given use of recursion it feels like bugs are just waiting to happen due to this | 0 |
43,429 | 11,219,496,484 | IssuesEvent | 2020-01-07 14:01:07 | UniFormal/MMT | https://api.github.com/repos/UniFormal/MMT | opened | lf-scala should account for case-insensitive name clashes in MMT theories | bug build system needs-design | Currently in LATIN2 we have a theory `Nat` containing two constant declarations named `Nat` and `nat`. This will produce something along the lines of
```scala
object Nat extends TheoryScala {
object nat extends ConstantScala { /* ... */ }
object Nat extends ConstantScala { /* ... */ }
}
```
which is a problem on case-insensitive filenames. | 1.0 | lf-scala should account for case-insensitive name clashes in MMT theories - Currently in LATIN2 we have a theory `Nat` containing two constant declarations named `Nat` and `nat`. This will produce something along the lines of
```scala
object Nat extends TheoryScala {
object nat extends ConstantScala { /* ... */ }
object Nat extends ConstantScala { /* ... */ }
}
```
which is a problem on case-insensitive filenames. | non_priority | lf scala should account for case insensitive name clashes in mmt theories currently in we have a theory nat containing two constant declarations named nat and nat this will produce something along the lines of scala object nat extends theoryscala object nat extends constantscala object nat extends constantscala which is a problem on case insensitive filenames | 0 |
146,187 | 13,173,374,135 | IssuesEvent | 2020-08-11 20:11:47 | MLH-Fellowship/nodemaker | https://api.github.com/repos/MLH-Fellowship/nodemaker | closed | Single installation command for frontend and backend dependencies | DX backend documentation | Docs would need to be updated as well. | 1.0 | Single installation command for frontend and backend dependencies - Docs would need to be updated as well. | non_priority | single installation command for frontend and backend dependencies docs would need to be updated as well | 0 |
3,099 | 6,024,836,348 | IssuesEvent | 2017-06-08 06:54:24 | Yoast/wordpress-seo | https://api.github.com/repos/Yoast/wordpress-seo | closed | [Wizard][Bug] Authorization Code window disappears almost immediately | compatibility | ### What did you expect to happen?
1. Click Authorize Google Account in the Wizard
1. Click the button
1. Google Permission Window Opens
1. Press Allow
1. Shows the authorization code and doesn't close until press close.
### What happened instead?
Final step lasted for less than half a second and then auto-closed. Had to Screenshot it at lightning speed in order to get the code.
### How can we reproduce this behavior?
On a site without authorization, start the wizard
### Technical info
* WordPress version: 4.7.5
* Yoast SEO version: 4.9
| True | [Wizard][Bug] Authorization Code window disappears almost immediately - ### What did you expect to happen?
1. Click Authorize Google Account in the Wizard
1. Click the button
1. Google Permission Window Opens
1. Press Allow
1. Shows the authorization code and doesn't close until press close.
### What happened instead?
Final step lasted for less than half a second and then auto-closed. Had to Screenshot it at lightning speed in order to get the code.
### How can we reproduce this behavior?
On a site without authorization, start the wizard
### Technical info
* WordPress version: 4.7.5
* Yoast SEO version: 4.9
| non_priority | authorization code window disappears almost immediately what did you expect to happen click authorize google account in the wizard click the button google permission window opens press allow shows the authorization code and doesn t close until press close what happened instead final step lasted for less than half a second and then auto closed had to screenshot it at lightning speed in order to get the code how can we reproduce this behavior on a site without authorization start the wizard technical info wordpress version yoast seo version | 0 |
94,274 | 11,860,503,617 | IssuesEvent | 2020-03-25 14:59:20 | phetsims/molecules-and-light | https://api.github.com/repos/phetsims/molecules-and-light | closed | Consider no "pop-up" for Dialog Buttons | design:a11y dev:a11y | Some screen readers (at least Voice Over) describes `aria-haspopup = "true"` as a menu pop-up. For VoiceOver users the PhET Menu button is the perfect example of pop-up button, whereas the Light Source Spectrum as a pop-up button is confusing.
We could/should re-investigate to see what the latest supported option there is for buttons that pop-up dialogs. For example, it this well supported?
- `aria-haspopup = "dialog"`
And consider not using `aria-haspopup = "true"` only for menu-type things that pop-up a list of options.
| 1.0 | Consider no "pop-up" for Dialog Buttons - Some screen readers (at least Voice Over) describes `aria-haspopup = "true"` as a menu pop-up. For VoiceOver users the PhET Menu button is the perfect example of pop-up button, whereas the Light Source Spectrum as a pop-up button is confusing.
We could/should re-investigate to see what the latest supported option there is for buttons that pop-up dialogs. For example, it this well supported?
- `aria-haspopup = "dialog"`
And consider not using `aria-haspopup = "true"` only for menu-type things that pop-up a list of options.
| non_priority | consider no pop up for dialog buttons some screen readers at least voice over describes aria haspopup true as a menu pop up for voiceover users the phet menu button is the perfect example of pop up button whereas the light source spectrum as a pop up button is confusing we could should re investigate to see what the latest supported option there is for buttons that pop up dialogs for example it this well supported aria haspopup dialog and consider not using aria haspopup true only for menu type things that pop up a list of options | 0 |
121,948 | 12,137,742,358 | IssuesEvent | 2020-04-23 16:09:15 | raini-dev/raini | https://api.github.com/repos/raini-dev/raini | closed | Add external links to README.md | GCPPR documentation | ### Twitter
[](https://twitter.com/raini_dev)
```markdown
[](https://twitter.com/raini_dev)
```
### Slack
[](https://raini-dev.slack.com)
```markdown
[](https://raini-dev.slack.com)
```
### Trello
[](https://trello.com/b/a7od8aCi/raini-workshops-schedule)
```markdown
[](https://trello.com/b/a7od8aCi/raini-workshops-schedule)
``` | 1.0 | Add external links to README.md - ### Twitter
[](https://twitter.com/raini_dev)
```markdown
[](https://twitter.com/raini_dev)
```
### Slack
[](https://raini-dev.slack.com)
```markdown
[](https://raini-dev.slack.com)
```
### Trello
[](https://trello.com/b/a7od8aCi/raini-workshops-schedule)
```markdown
[](https://trello.com/b/a7od8aCi/raini-workshops-schedule)
``` | non_priority | add external links to readme md twitter markdown slack markdown trello markdown | 0 |
390,244 | 26,854,957,849 | IssuesEvent | 2023-02-03 13:58:47 | themesberg/flowbite | https://api.github.com/repos/themesberg/flowbite | closed | Write Astro integration guide | documentation help wanted | **Is your feature request related to a problem? Please describe.**
Write an integration guide on the official documentation for using [Astro JS](https://astro.build/), Tailwind CSS, and Flowbite.
**Describe the solution you'd like**
Create a new `astro.md` file and based on the structure of other integration guides (ie. [TypeScript](https://flowbite.com/docs/getting-started/typescript/)) write a guide using this structure:
1. Introduction to Astro & what companies use it
2. Create a new Astro project
3. Install and configure Tailwind CSS with Astro
4. Install and configure Flowbite
5. Showcase Flowbite components and example
6. Starter project repository with MIT License
**Describe alternatives you've considered**
None.
**Additional context**
None. | 1.0 | Write Astro integration guide - **Is your feature request related to a problem? Please describe.**
Write an integration guide on the official documentation for using [Astro JS](https://astro.build/), Tailwind CSS, and Flowbite.
**Describe the solution you'd like**
Create a new `astro.md` file and based on the structure of other integration guides (ie. [TypeScript](https://flowbite.com/docs/getting-started/typescript/)) write a guide using this structure:
1. Introduction to Astro & what companies use it
2. Create a new Astro project
3. Install and configure Tailwind CSS with Astro
4. Install and configure Flowbite
5. Showcase Flowbite components and example
6. Starter project repository with MIT License
**Describe alternatives you've considered**
None.
**Additional context**
None. | non_priority | write astro integration guide is your feature request related to a problem please describe write an integration guide on the official documentation for using tailwind css and flowbite describe the solution you d like create a new astro md file and based on the structure of other integration guides ie write a guide using this structure introduction to astro what companies use it create a new astro project install and configure tailwind css with astro install and configure flowbite showcase flowbite components and example starter project repository with mit license describe alternatives you ve considered none additional context none | 0 |
131,698 | 12,488,860,126 | IssuesEvent | 2020-05-31 16:08:26 | tinkerhub-org/tinkerhub-portal | https://api.github.com/repos/tinkerhub-org/tinkerhub-portal | opened | Update README with project details | documentation | Update README with a description about the project. Include,
- A line or two about the project.
- Its purpose | 1.0 | Update README with project details - Update README with a description about the project. Include,
- A line or two about the project.
- Its purpose | non_priority | update readme with project details update readme with a description about the project include a line or two about the project its purpose | 0 |
32,295 | 6,759,187,095 | IssuesEvent | 2017-10-24 16:17:02 | primefaces/primeng | https://api.github.com/repos/primefaces/primeng | closed | Property Visible in menumodel does not work, Im using menubar | confirmed defect | ### There is no guarantee in receiving a response in GitHub Issue Tracker, If you'd like to secure our response, you may consider *PrimeNG PRO Support* where support is provided within 4 business hours
**I'm submitting a ...** (check one with "x")
```
[X ] bug report => Search github for a similar issue or PR before submitting
[ ] feature request => Please check if request is not on the roadmap already https://github.com/primefaces/primeng/wiki/Roadmap
[ ] support request => Please do not submit support request here, instead see http://forum.primefaces.org/viewforum.php?f=35
```
**Current behavior**
{ label: 'logout', icon: 'fa-pencil', visible: true, command: () => { this.logout() }},
{label: 'logout2', icon: 'fa-pencil', visible: false, command: () => { this.logout() } }
Both are visible
**Expected behavior**
Only the first one option visible 'logout"
**Minimal reproduction of the problem with instructions**
<!--
If the current behavior is a bug or you can illustrate your feature request better with an example,
please provide the *STEPS TO REPRODUCE* and if possible a *MINIMAL DEMO* of the problem via
https://plnkr.co or similar (you can use this template as a starting point: http://plnkr.co/edit/tpl:AvJOMERrnz94ekVua0u5).
-->
**What is the motivation / use case for changing the behavior?**
<!-- Describe the motivation or the concrete use case -->
**Please tell us about your environment:**
<!-- Operating system, IDE, package manager, HTTP server, ... -->
* **Angular version:** 4.3.6
<!-- Check whether this is still an issue in the most recent Angular version -->
* **PrimeNG version:** 4.2.2
<!-- Check whether this is still an issue in the most recent Angular version -->
* **Browser:** [all | Chrome XX | Firefox XX | IE XX | Safari XX | Mobile Chrome XX | Android X.X Web Browser | iOS XX Safari | iOS XX UIWebView | iOS XX WKWebView ]
<!-- All browsers where this could be reproduced -->
* **Language:** [all | TypeScript X.X | ES6/7 | ES5]
* **Node (for AoT issues):** `node --version` =
| 1.0 | Property Visible in menumodel does not work, Im using menubar - ### There is no guarantee in receiving a response in GitHub Issue Tracker, If you'd like to secure our response, you may consider *PrimeNG PRO Support* where support is provided within 4 business hours
**I'm submitting a ...** (check one with "x")
```
[X ] bug report => Search github for a similar issue or PR before submitting
[ ] feature request => Please check if request is not on the roadmap already https://github.com/primefaces/primeng/wiki/Roadmap
[ ] support request => Please do not submit support request here, instead see http://forum.primefaces.org/viewforum.php?f=35
```
**Current behavior**
{ label: 'logout', icon: 'fa-pencil', visible: true, command: () => { this.logout() }},
{label: 'logout2', icon: 'fa-pencil', visible: false, command: () => { this.logout() } }
Both are visible
**Expected behavior**
Only the first one option visible 'logout"
**Minimal reproduction of the problem with instructions**
<!--
If the current behavior is a bug or you can illustrate your feature request better with an example,
please provide the *STEPS TO REPRODUCE* and if possible a *MINIMAL DEMO* of the problem via
https://plnkr.co or similar (you can use this template as a starting point: http://plnkr.co/edit/tpl:AvJOMERrnz94ekVua0u5).
-->
**What is the motivation / use case for changing the behavior?**
<!-- Describe the motivation or the concrete use case -->
**Please tell us about your environment:**
<!-- Operating system, IDE, package manager, HTTP server, ... -->
* **Angular version:** 4.3.6
<!-- Check whether this is still an issue in the most recent Angular version -->
* **PrimeNG version:** 4.2.2
<!-- Check whether this is still an issue in the most recent Angular version -->
* **Browser:** [all | Chrome XX | Firefox XX | IE XX | Safari XX | Mobile Chrome XX | Android X.X Web Browser | iOS XX Safari | iOS XX UIWebView | iOS XX WKWebView ]
<!-- All browsers where this could be reproduced -->
* **Language:** [all | TypeScript X.X | ES6/7 | ES5]
* **Node (for AoT issues):** `node --version` =
| non_priority | property visible in menumodel does not work im using menubar there is no guarantee in receiving a response in github issue tracker if you d like to secure our response you may consider primeng pro support where support is provided within business hours i m submitting a check one with x bug report search github for a similar issue or pr before submitting feature request please check if request is not on the roadmap already support request please do not submit support request here instead see current behavior label logout icon fa pencil visible true command this logout label icon fa pencil visible false command this logout both are visible expected behavior only the first one option visible logout minimal reproduction of the problem with instructions if the current behavior is a bug or you can illustrate your feature request better with an example please provide the steps to reproduce and if possible a minimal demo of the problem via or similar you can use this template as a starting point what is the motivation use case for changing the behavior please tell us about your environment angular version primeng version browser language node for aot issues node version | 0 |
236,446 | 19,542,153,791 | IssuesEvent | 2022-01-01 04:51:08 | ImpowerGames/impower | https://api.github.com/repos/ImpowerGames/impower | closed | Test Endpoint - Legacy Users Can't Post New Pitches | ready for review bug: test | **Describe the bug**
A clear and concise description of what the bug is.
**Steps To Reproduce**
1. Log Into Legacy Account
2. Create a pitch
3. Permission Denied Error | 1.0 | Test Endpoint - Legacy Users Can't Post New Pitches - **Describe the bug**
A clear and concise description of what the bug is.
**Steps To Reproduce**
1. Log Into Legacy Account
2. Create a pitch
3. Permission Denied Error | non_priority | test endpoint legacy users can t post new pitches describe the bug a clear and concise description of what the bug is steps to reproduce log into legacy account create a pitch permission denied error | 0 |
3,295 | 4,208,980,736 | IssuesEvent | 2016-06-29 02:01:49 | servo/servo | https://api.github.com/repos/servo/servo | closed | Mac packager doesn't relink dylibs properly | A-browserhtml/P1 A-infrastructure | The mac packager does not properly relink all the dylibs together with `install_name_tool`. This means Servo will not run on machines without non-standard libs installed, like harfbuzz. | 1.0 | Mac packager doesn't relink dylibs properly - The mac packager does not properly relink all the dylibs together with `install_name_tool`. This means Servo will not run on machines without non-standard libs installed, like harfbuzz. | non_priority | mac packager doesn t relink dylibs properly the mac packager does not properly relink all the dylibs together with install name tool this means servo will not run on machines without non standard libs installed like harfbuzz | 0 |
430,228 | 30,122,189,605 | IssuesEvent | 2023-06-30 16:03:53 | gravitational/teleport | https://api.github.com/repos/gravitational/teleport | closed | Add key guides to setting up Teleport Cloud environment via Terraform | documentation | ## Applies To
- A new top-level section related to joining services to a cluster and setting up an agent pool
- A new top-level section related to configuring dynamic resources
## Related Issues
This issue fulfills part of #27379
## How will we know this is resolved?
_See the Details section below for context_
- There's a top-level docs section on joining services to the Teleport cluster with relevant guides included in the section
- There's a guide to deploying an agent pool with Terraform in the section above
- There is a guide to deploying dynamic infra resources in the section above
- There is a top-level docs section on applying dynamic configuration resources
- There are instructions in the section above to applying roles and SSO connectors via Terraform
## Details
This issue focuses on the "toy/terraform/self-hosted" and
"cloud/production/terraform" learning tracks described in #27379. We can group
these tracks because they involve the fastest ways to get started with Teleport:
setting up a toy self-hosted cluster and getting started with a scalable
Teleport Team/Teleport Cloud experience.
Note that with this approach, we can also condense the "cloud/toy/terraform" and
"cloud/production/terraform" tracks.
### Content to write
We need to determine how to translate the steps of using IAC to follow
the \"toy/terraform/self-hosted\" and \"cloud/production/terraform\"
tracks into content within the documentation.
#### Deploy an agent pool with Terraform/Enroll dynamic resources with Terraform
I think it would make sense to:
- Elevate the current \"[Join Services to your Teleport
Cluster](https://goteleport.com/docs/management/join-services-to-your-cluster/)\"
section to a top-level docs section, as it\'s a key part of
setting up a cluster.
- Add a \"Deploy an Agent Pool\" guide to this section. This explains
how an agent pool works (i.e., agents can proxy several resources,
which operators can adjust dynamically or via IAC). It also shows
you how to launch an agent pool via Terraform.
- Add a guide to enrolling dynamic infrastructure resources (e.g.,
applications and Kubernetes clusters) with Terraform to the \"Join
Services\" section.
#### Manage RBAC resources with Terraform
We already have a guide to [setting up the Terraform provider](https://goteleport.com/docs/management/guides/terraform-provider/)
to manage resources. We can make this more prominent in the
documentation by moving it from \"/docs/management/guides\" to a
top-level section related to dynamic configuration resources.
I have a [PR in progress](https://github.com/gravitational/teleport/pull/25442)
to add a section of the docs related to dynamic configuration resources,
and we can make it a top-level section of the docs. This contains how-to
guides for the Terraform provider and Kubernetes operator.
We can add a guide to this section that provides examples of roles and
SSO connectors to create with our Terraform provider. | 1.0 | Add key guides to setting up Teleport Cloud environment via Terraform - ## Applies To
- A new top-level section related to joining services to a cluster and setting up an agent pool
- A new top-level section related to configuring dynamic resources
## Related Issues
This issue fulfills part of #27379
## How will we know this is resolved?
_See the Details section below for context_
- There's a top-level docs section on joining services to the Teleport cluster with relevant guides included in the section
- There's a guide to deploying an agent pool with Terraform in the section above
- There is a guide to deploying dynamic infra resources in the section above
- There is a top-level docs section on applying dynamic configuration resources
- There are instructions in the section above to applying roles and SSO connectors via Terraform
## Details
This issue focuses on the "toy/terraform/self-hosted" and
"cloud/production/terraform" learning tracks described in #27379. We can group
these tracks because they involve the fastest ways to get started with Teleport:
setting up a toy self-hosted cluster and getting started with a scalable
Teleport Team/Teleport Cloud experience.
Note that with this approach, we can also condense the "cloud/toy/terraform" and
"cloud/production/terraform" tracks.
### Content to write
We need to determine how to translate the steps of using IAC to follow
the \"toy/terraform/self-hosted\" and \"cloud/production/terraform\"
tracks into content within the documentation.
#### Deploy an agent pool with Terraform/Enroll dynamic resources with Terraform
I think it would make sense to:
- Elevate the current \"[Join Services to your Teleport
Cluster](https://goteleport.com/docs/management/join-services-to-your-cluster/)\"
section to a top-level docs section, as it\'s a key part of
setting up a cluster.
- Add a \"Deploy an Agent Pool\" guide to this section. This explains
how an agent pool works (i.e., agents can proxy several resources,
which operators can adjust dynamically or via IAC). It also shows
you how to launch an agent pool via Terraform.
- Add a guide to enrolling dynamic infrastructure resources (e.g.,
applications and Kubernetes clusters) with Terraform to the \"Join
Services\" section.
#### Manage RBAC resources with Terraform
We already have a guide to [setting up the Terraform provider](https://goteleport.com/docs/management/guides/terraform-provider/)
to manage resources. We can make this more prominent in the
documentation by moving it from \"/docs/management/guides\" to a
top-level section related to dynamic configuration resources.
I have a [PR in progress](https://github.com/gravitational/teleport/pull/25442)
to add a section of the docs related to dynamic configuration resources,
and we can make it a top-level section of the docs. This contains how-to
guides for the Terraform provider and Kubernetes operator.
We can add a guide to this section that provides examples of roles and
SSO connectors to create with our Terraform provider. | non_priority | add key guides to setting up teleport cloud environment via terraform applies to a new top level section related to joining services to a cluster and setting up an agent pool a new top level section related to configuring dynamic resources related issues this issue fulfills part of how will we know this is resolved see the details section below for context there s a top level docs section on joining services to the teleport cluster with relevant guides included in the section there s a guide to deploying an agent pool with terraform in the section above there is a guide to deploying dynamic infra resources in the section above there is a top level docs section on applying dynamic configuration resources there are instructions in the section above to applying roles and sso connectors via terraform details this issue focuses on the toy terraform self hosted and cloud production terraform learning tracks described in we can group these tracks because they involve the fastest ways to get started with teleport setting up a toy self hosted cluster and getting started with a scalable teleport team teleport cloud experience note that with this approach we can also condense the cloud toy terraform and cloud production terraform tracks content to write we need to determine how to translate the steps of using iac to follow the toy terraform self hosted and cloud production terraform tracks into content within the documentation deploy an agent pool with terraform enroll dynamic resources with terraform i think it would make sense to elevate the current join services to your teleport cluster section to a top level docs section as it s a key part of setting up a cluster add a deploy an agent pool guide to this section this explains how an agent pool works i e agents can proxy several resources which operators can adjust dynamically or via iac it also shows you how to launch an agent pool via terraform add a guide to enrolling dynamic infrastructure resources e g applications and kubernetes clusters with terraform to the join services section manage rbac resources with terraform we already have a guide to to manage resources we can make this more prominent in the documentation by moving it from docs management guides to a top level section related to dynamic configuration resources i have a to add a section of the docs related to dynamic configuration resources and we can make it a top level section of the docs this contains how to guides for the terraform provider and kubernetes operator we can add a guide to this section that provides examples of roles and sso connectors to create with our terraform provider | 0 |
155,698 | 12,267,586,510 | IssuesEvent | 2020-05-07 10:57:32 | IMA-WorldHealth/bhima | https://api.github.com/repos/IMA-WorldHealth/bhima | opened | Add official support for MySQL 8 | Feature Request tests | Thanks to the work done by @individual-it, we know that MySQL 8 isn't supported. In fact, only MySQL 5.7 is supported. We've done the documentation updates to reflect this, but we should make the effort to target MySQL 8. As pointed out by @individual-it in https://github.com/IMA-WorldHealth/bhima/issues/4393, Ubuntu 20.04 LTS ships with [MySQL 8 by default](https://www.digitalocean.com/community/tutorials/how-to-install-mysql-on-ubuntu-20-04#step-1-%E2%80%94-installing-mysql).
Let's put in first-class support for MySQL 8. For now, the only things that have been established are that the `PASSWORD()` function has been removed. It looks like we [can use a work-around](https://stackoverflow.com/a/60243956) while we set up a migration plan for our existing installations. We'll just create the PASSWORD() function if it doesn't exist using the SO suggestions.
Once we have the workaround in place, we'll need to run the tests on MySQL 8 in a CI environment to ensure they continue working.
This issue will remain open until we've got the tests up and running. | 1.0 | Add official support for MySQL 8 - Thanks to the work done by @individual-it, we know that MySQL 8 isn't supported. In fact, only MySQL 5.7 is supported. We've done the documentation updates to reflect this, but we should make the effort to target MySQL 8. As pointed out by @individual-it in https://github.com/IMA-WorldHealth/bhima/issues/4393, Ubuntu 20.04 LTS ships with [MySQL 8 by default](https://www.digitalocean.com/community/tutorials/how-to-install-mysql-on-ubuntu-20-04#step-1-%E2%80%94-installing-mysql).
Let's put in first-class support for MySQL 8. For now, the only things that have been established are that the `PASSWORD()` function has been removed. It looks like we [can use a work-around](https://stackoverflow.com/a/60243956) while we set up a migration plan for our existing installations. We'll just create the PASSWORD() function if it doesn't exist using the SO suggestions.
Once we have the workaround in place, we'll need to run the tests on MySQL 8 in a CI environment to ensure they continue working.
This issue will remain open until we've got the tests up and running. | non_priority | add official support for mysql thanks to the work done by individual it we know that mysql isn t supported in fact only mysql is supported we ve done the documentation updates to reflect this but we should make the effort to target mysql as pointed out by individual it in ubuntu lts ships with let s put in first class support for mysql for now the only things that have been established are that the password function has been removed it looks like we while we set up a migration plan for our existing installations we ll just create the password function if it doesn t exist using the so suggestions once we have the workaround in place we ll need to run the tests on mysql in a ci environment to ensure they continue working this issue will remain open until we ve got the tests up and running | 0 |
90,950 | 10,704,423,760 | IssuesEvent | 2019-10-24 11:42:40 | alan-turing-institute/sktime | https://api.github.com/repos/alan-turing-institute/sktime | closed | Documentation needs to be fixed | documentation | Single comment line on `sktime.utils.validation.forecasting` needs to be fixed. Check the image below.
Instead of `<<<<<<< HEAD:sktime/utils/validation/forecasting.py` we should see `Returns`.
 | 1.0 | Documentation needs to be fixed - Single comment line on `sktime.utils.validation.forecasting` needs to be fixed. Check the image below.
Instead of `<<<<<<< HEAD:sktime/utils/validation/forecasting.py` we should see `Returns`.
 | non_priority | documentation needs to be fixed single comment line on sktime utils validation forecasting needs to be fixed check the image below instead of head sktime utils validation forecasting py we should see returns | 0 |
137,508 | 30,705,915,324 | IssuesEvent | 2023-07-27 06:08:05 | flutter/flutter | https://api.github.com/repos/flutter/flutter | closed | Triage process self-test | team-codelabs will need additional triage team-infra P2 team-google-testing team-release team-news team-design | This is a test of our triage processes.
Please handle this issue the same way you would a normal valid but low-priority issue.
For more details see https://github.com/flutter/flutter/wiki/Triage | 1.0 | Triage process self-test - This is a test of our triage processes.
Please handle this issue the same way you would a normal valid but low-priority issue.
For more details see https://github.com/flutter/flutter/wiki/Triage | non_priority | triage process self test this is a test of our triage processes please handle this issue the same way you would a normal valid but low priority issue for more details see | 0 |
76,227 | 14,583,116,297 | IssuesEvent | 2020-12-18 13:30:22 | odpi/egeria | https://api.github.com/repos/odpi/egeria | opened | Security Analysis - System Information Leak | code-quality security | Ubrella issue for Code quality improvements identified
System Information Leak. | 1.0 | Security Analysis - System Information Leak - Ubrella issue for Code quality improvements identified
System Information Leak. | non_priority | security analysis system information leak ubrella issue for code quality improvements identified system information leak | 0 |
19,208 | 5,824,907,564 | IssuesEvent | 2017-05-07 16:59:19 | ggez/ggez | https://api.github.com/repos/ggez/ggez | opened | implement various unimplemented things in graphics | enhancement [CODE] | Most of them are pretty easy, don't sweat the rest. | 1.0 | implement various unimplemented things in graphics - Most of them are pretty easy, don't sweat the rest. | non_priority | implement various unimplemented things in graphics most of them are pretty easy don t sweat the rest | 0 |
26,206 | 26,556,766,716 | IssuesEvent | 2023-01-20 12:43:18 | bigbluebutton/bigbluebutton | https://api.github.com/repos/bigbluebutton/bigbluebutton | closed | After moving a student to a different breakout room, close the obsolete tab | module: client component: breakout rooms target: usability | <!--PLEASE DO NOT FILE ISSUES FOR GENERAL SUPPORT QUESTIONS.
This issue tracker is only for bbb development related issues.-->
**Describe the bug**
When you move a viewer from breakout roomA to breakout roomB, the viewer will be stuck seeing
**To Reproduce**
Steps to reproduce the behavior:
1. Join a meeting as a moderator M
2. Join the meeting as a viewer V
3. M starts a breakout session and puts V in room1
4. V joins room1 (it opens in a new tab)
5. M selects Manage users from the breakouts 3 dot menu and moves V from room1 to room2
**Expected behavior**
V is joining room2, no longer seeing room1.
**Actual behavior**
V is actually stuck seeing a 403 screen that it was removed from the meeting. The user is supposed to notice that **the tab can be closed** and in the main room V is getting invited to room2
Can we close the tab for room1 automatically?
**Screenshots**
**BBB version:**
BigBlueButton 2.6.0-beta.2 | True | After moving a student to a different breakout room, close the obsolete tab - <!--PLEASE DO NOT FILE ISSUES FOR GENERAL SUPPORT QUESTIONS.
This issue tracker is only for bbb development related issues.-->
**Describe the bug**
When you move a viewer from breakout roomA to breakout roomB, the viewer will be stuck seeing
**To Reproduce**
Steps to reproduce the behavior:
1. Join a meeting as a moderator M
2. Join the meeting as a viewer V
3. M starts a breakout session and puts V in room1
4. V joins room1 (it opens in a new tab)
5. M selects Manage users from the breakouts 3 dot menu and moves V from room1 to room2
**Expected behavior**
V is joining room2, no longer seeing room1.
**Actual behavior**
V is actually stuck seeing a 403 screen that it was removed from the meeting. The user is supposed to notice that **the tab can be closed** and in the main room V is getting invited to room2
Can we close the tab for room1 automatically?
**Screenshots**
**BBB version:**
BigBlueButton 2.6.0-beta.2 | non_priority | after moving a student to a different breakout room close the obsolete tab please do not file issues for general support questions this issue tracker is only for bbb development related issues describe the bug when you move a viewer from breakout rooma to breakout roomb the viewer will be stuck seeing to reproduce steps to reproduce the behavior join a meeting as a moderator m join the meeting as a viewer v m starts a breakout session and puts v in v joins it opens in a new tab m selects manage users from the breakouts dot menu and moves v from to expected behavior v is joining no longer seeing actual behavior v is actually stuck seeing a screen that it was removed from the meeting the user is supposed to notice that the tab can be closed and in the main room v is getting invited to can we close the tab for automatically screenshots bbb version bigbluebutton beta | 0 |
163,717 | 20,364,050,554 | IssuesEvent | 2022-02-21 02:02:28 | rgordon95/github-search-redux-thunk | https://api.github.com/repos/rgordon95/github-search-redux-thunk | closed | CVE-2022-0512 (High) detected in url-parse-1.4.7.tgz - autoclosed | security vulnerability | ## CVE-2022-0512 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.4.7.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz</a></p>
<p>Path to dependency file: /github-search-redux-thunk/package.json</p>
<p>Path to vulnerable library: /node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.0.1.tgz (Root Library)
- react-dev-utils-9.0.1.tgz
- sockjs-client-1.3.0.tgz
- :x: **url-parse-1.4.7.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Authorization Bypass Through User-Controlled Key in NPM url-parse prior to 1.5.6.
<p>Publish Date: 2022-02-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0512>CVE-2022-0512</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0512">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0512</a></p>
<p>Release Date: 2022-02-14</p>
<p>Fix Resolution: url-parse - 1.5.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-0512 (High) detected in url-parse-1.4.7.tgz - autoclosed - ## CVE-2022-0512 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.4.7.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz</a></p>
<p>Path to dependency file: /github-search-redux-thunk/package.json</p>
<p>Path to vulnerable library: /node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.0.1.tgz (Root Library)
- react-dev-utils-9.0.1.tgz
- sockjs-client-1.3.0.tgz
- :x: **url-parse-1.4.7.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Authorization Bypass Through User-Controlled Key in NPM url-parse prior to 1.5.6.
<p>Publish Date: 2022-02-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0512>CVE-2022-0512</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0512">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0512</a></p>
<p>Release Date: 2022-02-14</p>
<p>Fix Resolution: url-parse - 1.5.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in url parse tgz autoclosed cve high severity vulnerability vulnerable library url parse tgz small footprint url parser that works seamlessly across node js and browser environments library home page a href path to dependency file github search redux thunk package json path to vulnerable library node modules url parse package json dependency hierarchy react scripts tgz root library react dev utils tgz sockjs client tgz x url parse tgz vulnerable library vulnerability details authorization bypass through user controlled key in npm url parse prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution url parse step up your open source security game with whitesource | 0 |
189,548 | 14,513,670,532 | IssuesEvent | 2020-12-13 05:41:45 | kalexmills/github-vet-tests-dec2020 | https://api.github.com/repos/kalexmills/github-vet-tests-dec2020 | closed | grafana/snap-plugin-collector-kubestate: kubestate/pod_test.go; 3 LoC | fresh test tiny |
Found a possible issue in [grafana/snap-plugin-collector-kubestate](https://www.github.com/grafana/snap-plugin-collector-kubestate) at [kubestate/pod_test.go](https://github.com/grafana/snap-plugin-collector-kubestate/blob/8d5267c90eca313512e7d0479bf61cf7bbbcdd64/kubestate/pod_test.go#L196-L198)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to metric at line 197 may start a goroutine
[Click here to see the code in its original context.](https://github.com/grafana/snap-plugin-collector-kubestate/blob/8d5267c90eca313512e7d0479bf61cf7bbbcdd64/kubestate/pod_test.go#L196-L198)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for i, metric := range metrics {
So(format(&metric), ShouldEqual, c.expected[i])
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 8d5267c90eca313512e7d0479bf61cf7bbbcdd64
| 1.0 | grafana/snap-plugin-collector-kubestate: kubestate/pod_test.go; 3 LoC -
Found a possible issue in [grafana/snap-plugin-collector-kubestate](https://www.github.com/grafana/snap-plugin-collector-kubestate) at [kubestate/pod_test.go](https://github.com/grafana/snap-plugin-collector-kubestate/blob/8d5267c90eca313512e7d0479bf61cf7bbbcdd64/kubestate/pod_test.go#L196-L198)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to metric at line 197 may start a goroutine
[Click here to see the code in its original context.](https://github.com/grafana/snap-plugin-collector-kubestate/blob/8d5267c90eca313512e7d0479bf61cf7bbbcdd64/kubestate/pod_test.go#L196-L198)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for i, metric := range metrics {
So(format(&metric), ShouldEqual, c.expected[i])
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 8d5267c90eca313512e7d0479bf61cf7bbbcdd64
| non_priority | grafana snap plugin collector kubestate kubestate pod test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message function call which takes a reference to metric at line may start a goroutine click here to show the line s of go which triggered the analyzer go for i metric range metrics so format metric shouldequal c expected leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 0 |
294,540 | 25,380,192,806 | IssuesEvent | 2022-11-21 16:56:23 | NationalSecurityAgency/skills-service | https://api.github.com/repos/NationalSecurityAgency/skills-service | closed | Global badge skills table mistakenly show ``Manage`` button for the skill that was added | bug test | - navigate to ``/administrator/globalBadges/<global_badge_id/``
- add a skill
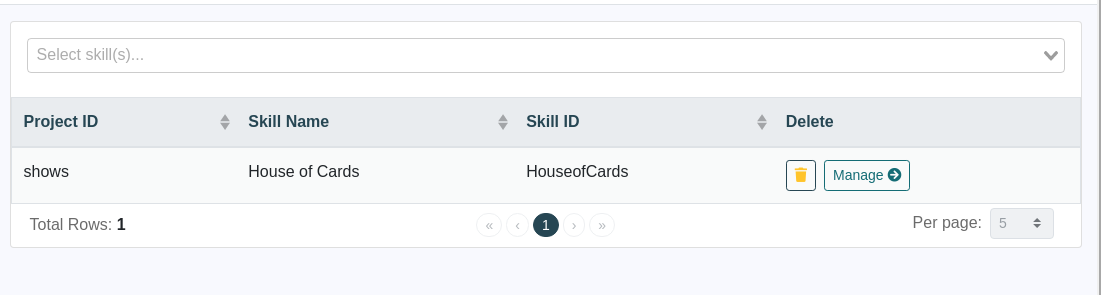
- ``Manage`` button is mistakenly displayed
- Refresh and the button is gone | 1.0 | Global badge skills table mistakenly show ``Manage`` button for the skill that was added - - navigate to ``/administrator/globalBadges/<global_badge_id/``
- add a skill
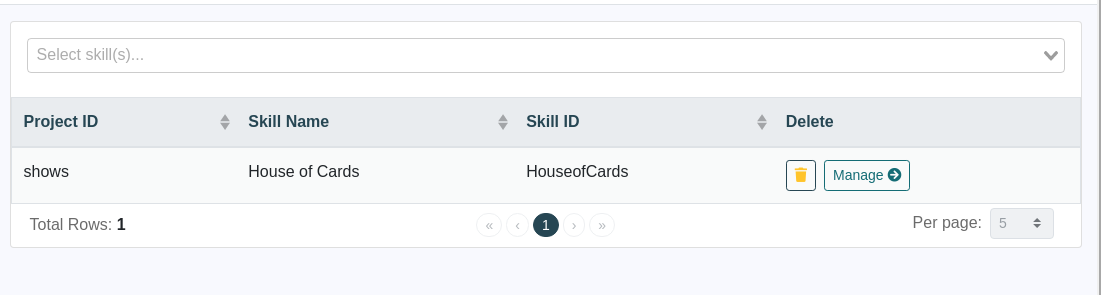
- ``Manage`` button is mistakenly displayed
- Refresh and the button is gone | non_priority | global badge skills table mistakenly show manage button for the skill that was added navigate to administrator globalbadges global badge id add a skill manage button is mistakenly displayed refresh and the button is gone | 0 |
441,359 | 30,779,774,294 | IssuesEvent | 2023-07-31 09:12:59 | i4Ds/Karabo-Pipeline | https://api.github.com/repos/i4Ds/Karabo-Pipeline | opened | Add instructions on how to cite Karabo and the packages it uses | documentation prio-high | Add either a section ("Citation" or "Citing") in the README, or a "citation.md" file, explaining how to cite Karabo and its underlying packages.
Remember to add citation guides for: `montage`, `OSKAR`, `Rascil`, `bluebild` and other packages being used. | 1.0 | Add instructions on how to cite Karabo and the packages it uses - Add either a section ("Citation" or "Citing") in the README, or a "citation.md" file, explaining how to cite Karabo and its underlying packages.
Remember to add citation guides for: `montage`, `OSKAR`, `Rascil`, `bluebild` and other packages being used. | non_priority | add instructions on how to cite karabo and the packages it uses add either a section citation or citing in the readme or a citation md file explaining how to cite karabo and its underlying packages remember to add citation guides for montage oskar rascil bluebild and other packages being used | 0 |
19,943 | 5,958,574,589 | IssuesEvent | 2017-05-29 08:23:00 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | [4.0] Tags links in default content 404 errors | No Code Attached Yet | ### Steps to reproduce the issue
install Joomla 4
Go to http://joomla4/index.php/all-tags
see:
<img width="757" alt="screen shot 2017-05-03 at 13 09 34" src="https://cloud.githubusercontent.com/assets/400092/25659887/c5317592-3001-11e7-95e2-903ddbec8433.png">
### Expected result
Clicking ANY of these tags takes me to a `200 OK` type page.
### Actual result
Green - http://joomla4/index.php/all-tags/green - 404 URL invalid
Lime - http://joomla4/index.php/all-tags/lime - 404 URL invalid
Red - http://joomla4/index.php/tagged-items - Probably not the right url to go to?
Yellow - http://joomla4/index.php/compact-tagged - surely yellow should be in the url ?
### System information (as much as possible)
### Additional comments
| 1.0 | [4.0] Tags links in default content 404 errors - ### Steps to reproduce the issue
install Joomla 4
Go to http://joomla4/index.php/all-tags
see:
<img width="757" alt="screen shot 2017-05-03 at 13 09 34" src="https://cloud.githubusercontent.com/assets/400092/25659887/c5317592-3001-11e7-95e2-903ddbec8433.png">
### Expected result
Clicking ANY of these tags takes me to a `200 OK` type page.
### Actual result
Green - http://joomla4/index.php/all-tags/green - 404 URL invalid
Lime - http://joomla4/index.php/all-tags/lime - 404 URL invalid
Red - http://joomla4/index.php/tagged-items - Probably not the right url to go to?
Yellow - http://joomla4/index.php/compact-tagged - surely yellow should be in the url ?
### System information (as much as possible)
### Additional comments
| non_priority | tags links in default content errors steps to reproduce the issue install joomla go to see img width alt screen shot at src expected result clicking any of these tags takes me to a ok type page actual result green url invalid lime url invalid red probably not the right url to go to yellow surely yellow should be in the url system information as much as possible additional comments | 0 |
45,451 | 11,671,557,594 | IssuesEvent | 2020-03-04 03:36:29 | MasoniteFramework/orm | https://api.github.com/repos/MasoniteFramework/orm | closed | Add ability to infer the table name | Query Builder | right now you need to set the `__table__` attribute. we need to be able to figure it out with the table name.
For example, the `User` model would be `users` table | 1.0 | Add ability to infer the table name - right now you need to set the `__table__` attribute. we need to be able to figure it out with the table name.
For example, the `User` model would be `users` table | non_priority | add ability to infer the table name right now you need to set the table attribute we need to be able to figure it out with the table name for example the user model would be users table | 0 |
260,143 | 27,768,671,556 | IssuesEvent | 2023-03-16 13:10:30 | pazhanivel07/OpenSSL_1_1_1g-Aosp10 | https://api.github.com/repos/pazhanivel07/OpenSSL_1_1_1g-Aosp10 | opened | CVE-2021-3449 (Medium) detected in OpenSSLOpenSSL_1_1_1g | Mend: dependency security vulnerability | ## CVE-2021-3449 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>OpenSSLOpenSSL_1_1_1g</b></p></summary>
<p>
<p>TLS/SSL and crypto library</p>
<p>Library home page: <a href=https://github.com/OpenSSL/OpenSSL.git>https://github.com/OpenSSL/OpenSSL.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/pazhanivel07/OpenSSL_1_1_1g-Aosp10/commit/430551726dcd8fc3efbd8baa6c1a1da135e18f13">430551726dcd8fc3efbd8baa6c1a1da135e18f13</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/ssl/statem/extensions.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An OpenSSL TLS server may crash if sent a maliciously crafted renegotiation ClientHello message from a client. If a TLSv1.2 renegotiation ClientHello omits the signature_algorithms extension (where it was present in the initial ClientHello), but includes a signature_algorithms_cert extension then a NULL pointer dereference will result, leading to a crash and a denial of service attack. A server is only vulnerable if it has TLSv1.2 and renegotiation enabled (which is the default configuration). OpenSSL TLS clients are not impacted by this issue. All OpenSSL 1.1.1 versions are affected by this issue. Users of these versions should upgrade to OpenSSL 1.1.1k. OpenSSL 1.0.2 is not impacted by this issue. Fixed in OpenSSL 1.1.1k (Affected 1.1.1-1.1.1j).
<p>Publish Date: 2021-03-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-3449>CVE-2021-3449</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-3449">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-3449</a></p>
<p>Release Date: 2021-03-25</p>
<p>Fix Resolution: 1.1.1k</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-3449 (Medium) detected in OpenSSLOpenSSL_1_1_1g - ## CVE-2021-3449 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>OpenSSLOpenSSL_1_1_1g</b></p></summary>
<p>
<p>TLS/SSL and crypto library</p>
<p>Library home page: <a href=https://github.com/OpenSSL/OpenSSL.git>https://github.com/OpenSSL/OpenSSL.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/pazhanivel07/OpenSSL_1_1_1g-Aosp10/commit/430551726dcd8fc3efbd8baa6c1a1da135e18f13">430551726dcd8fc3efbd8baa6c1a1da135e18f13</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/ssl/statem/extensions.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An OpenSSL TLS server may crash if sent a maliciously crafted renegotiation ClientHello message from a client. If a TLSv1.2 renegotiation ClientHello omits the signature_algorithms extension (where it was present in the initial ClientHello), but includes a signature_algorithms_cert extension then a NULL pointer dereference will result, leading to a crash and a denial of service attack. A server is only vulnerable if it has TLSv1.2 and renegotiation enabled (which is the default configuration). OpenSSL TLS clients are not impacted by this issue. All OpenSSL 1.1.1 versions are affected by this issue. Users of these versions should upgrade to OpenSSL 1.1.1k. OpenSSL 1.0.2 is not impacted by this issue. Fixed in OpenSSL 1.1.1k (Affected 1.1.1-1.1.1j).
<p>Publish Date: 2021-03-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-3449>CVE-2021-3449</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-3449">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-3449</a></p>
<p>Release Date: 2021-03-25</p>
<p>Fix Resolution: 1.1.1k</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in opensslopenssl cve medium severity vulnerability vulnerable library opensslopenssl tls ssl and crypto library library home page a href found in head commit a href found in base branch master vulnerable source files ssl statem extensions c vulnerability details an openssl tls server may crash if sent a maliciously crafted renegotiation clienthello message from a client if a renegotiation clienthello omits the signature algorithms extension where it was present in the initial clienthello but includes a signature algorithms cert extension then a null pointer dereference will result leading to a crash and a denial of service attack a server is only vulnerable if it has and renegotiation enabled which is the default configuration openssl tls clients are not impacted by this issue all openssl versions are affected by this issue users of these versions should upgrade to openssl openssl is not impacted by this issue fixed in openssl affected publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
53,386 | 13,804,174,738 | IssuesEvent | 2020-10-11 07:36:54 | drakeg/udemy_django_vue | https://api.github.com/repos/drakeg/udemy_django_vue | opened | CVE-2020-7693 (Medium) detected in sockjs-0.3.19.tgz | security vulnerability | ## CVE-2020-7693 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sockjs-0.3.19.tgz</b></p></summary>
<p>SockJS-node is a server counterpart of SockJS-client a JavaScript library that provides a WebSocket-like object in the browser. SockJS gives you a coherent, cross-browser, Javascript API which creates a low latency, full duplex, cross-domain communication</p>
<p>Library home page: <a href="https://registry.npmjs.org/sockjs/-/sockjs-0.3.19.tgz">https://registry.npmjs.org/sockjs/-/sockjs-0.3.19.tgz</a></p>
<p>
Dependency Hierarchy:
- cli-service-3.12.1.tgz (Root Library)
- webpack-dev-server-3.9.0.tgz
- :x: **sockjs-0.3.19.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/drakeg/udemy_django_vue/commit/bd1765a94788f869886afc951702e75b0fd3cd75">bd1765a94788f869886afc951702e75b0fd3cd75</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Incorrect handling of Upgrade header with the value websocket leads in crashing of containers hosting sockjs apps. This affects the package sockjs before 0.3.20.
<p>Publish Date: 2020-07-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7693>CVE-2020-7693</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sockjs/sockjs-node/pull/265">https://github.com/sockjs/sockjs-node/pull/265</a></p>
<p>Release Date: 2020-07-09</p>
<p>Fix Resolution: sockjs - 0.3.20</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-7693 (Medium) detected in sockjs-0.3.19.tgz - ## CVE-2020-7693 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sockjs-0.3.19.tgz</b></p></summary>
<p>SockJS-node is a server counterpart of SockJS-client a JavaScript library that provides a WebSocket-like object in the browser. SockJS gives you a coherent, cross-browser, Javascript API which creates a low latency, full duplex, cross-domain communication</p>
<p>Library home page: <a href="https://registry.npmjs.org/sockjs/-/sockjs-0.3.19.tgz">https://registry.npmjs.org/sockjs/-/sockjs-0.3.19.tgz</a></p>
<p>
Dependency Hierarchy:
- cli-service-3.12.1.tgz (Root Library)
- webpack-dev-server-3.9.0.tgz
- :x: **sockjs-0.3.19.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/drakeg/udemy_django_vue/commit/bd1765a94788f869886afc951702e75b0fd3cd75">bd1765a94788f869886afc951702e75b0fd3cd75</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Incorrect handling of Upgrade header with the value websocket leads in crashing of containers hosting sockjs apps. This affects the package sockjs before 0.3.20.
<p>Publish Date: 2020-07-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7693>CVE-2020-7693</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sockjs/sockjs-node/pull/265">https://github.com/sockjs/sockjs-node/pull/265</a></p>
<p>Release Date: 2020-07-09</p>
<p>Fix Resolution: sockjs - 0.3.20</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in sockjs tgz cve medium severity vulnerability vulnerable library sockjs tgz sockjs node is a server counterpart of sockjs client a javascript library that provides a websocket like object in the browser sockjs gives you a coherent cross browser javascript api which creates a low latency full duplex cross domain communication library home page a href dependency hierarchy cli service tgz root library webpack dev server tgz x sockjs tgz vulnerable library found in head commit a href vulnerability details incorrect handling of upgrade header with the value websocket leads in crashing of containers hosting sockjs apps this affects the package sockjs before publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution sockjs step up your open source security game with whitesource | 0 |
76,511 | 7,533,585,269 | IssuesEvent | 2018-04-16 03:24:40 | oscarrobotics/FRC2018-Giraffe | https://api.github.com/repos/oscarrobotics/FRC2018-Giraffe | closed | AutoIntakeElbow never finishing | bug needs testing | In this case, we may not be reaching steady-state, although the arm is in an acceptable position. We need to look at the setpoint vs. the actual position and decide if that's good enough, and put that error as acceptableError. | 1.0 | AutoIntakeElbow never finishing - In this case, we may not be reaching steady-state, although the arm is in an acceptable position. We need to look at the setpoint vs. the actual position and decide if that's good enough, and put that error as acceptableError. | non_priority | autointakeelbow never finishing in this case we may not be reaching steady state although the arm is in an acceptable position we need to look at the setpoint vs the actual position and decide if that s good enough and put that error as acceptableerror | 0 |
361,553 | 25,343,100,108 | IssuesEvent | 2022-11-19 00:26:43 | amzn/selling-partner-api-docs | https://api.github.com/repos/amzn/selling-partner-api-docs | closed | Orders API - getOrderItemsBuyerInfo response: BuyerCustomizedInfo.CustomizedURL is empty | bug Documentation Support Issue closing soon | When I try to get the customer's customized information, the returned field is empty
Has anyone encountered this situation?
Can help me?
This problem has been bothering me for many days | 1.0 | Orders API - getOrderItemsBuyerInfo response: BuyerCustomizedInfo.CustomizedURL is empty - When I try to get the customer's customized information, the returned field is empty
Has anyone encountered this situation?
Can help me?
This problem has been bothering me for many days | non_priority | orders api getorderitemsbuyerinfo response buyercustomizedinfo customizedurl is empty when i try to get the customer s customized information the returned field is empty has anyone encountered this situation can help me this problem has been bothering me for many days | 0 |
214,386 | 24,069,954,085 | IssuesEvent | 2022-09-18 02:40:10 | fecgov/openFEC | https://api.github.com/repos/fecgov/openFEC | closed | Check logs hackathon week | Security: general | Log review needs to be completed per the Security Event Review Checklist (https://github.com/fecgov/FEC/wiki/Security-Event-Review-Checklist)
Ref: [Check logs sprint 19.2 week 2 ](https://github.com/fecgov/openFEC/issues/5226) | True | Check logs hackathon week - Log review needs to be completed per the Security Event Review Checklist (https://github.com/fecgov/FEC/wiki/Security-Event-Review-Checklist)
Ref: [Check logs sprint 19.2 week 2 ](https://github.com/fecgov/openFEC/issues/5226) | non_priority | check logs hackathon week log review needs to be completed per the security event review checklist ref | 0 |
58,495 | 14,404,701,313 | IssuesEvent | 2020-12-03 17:38:26 | mozilla-mobile/focus-android | https://api.github.com/repos/mozilla-mobile/focus-android | closed | Code Quality task failing: unable to find pmd | build | I'm not sure how long this has been a problem, but I am trying to find out why UI tests are not being ran on Firebase currently (with whatever currently pass, that's another problem), but the Code Quality task is a dependency for the scheduled UI test task.
Code Quality Failure: https://firefox-ci-tc.services.mozilla.com/tasks/OohJuDmMT-iQ9rYdBo99NA/runs/0/logs/https%3A%2F%2Ffirefox-ci-tc.services.mozilla.com%2Fapi%2Fqueue%2Fv1%2Ftask%2FOohJuDmMT-iQ9rYdBo99NA%2Fruns%2F0%2Fartifacts%2Fpublic%2Flogs%2Flive.log
```Log
<======-------> 50% CONFIGURING [37s]> :app<=============> 100% CONFIGURING [37s]
FAILURE: Build failed with an exception.
* What went wrong:
Task 'pmd' not found in root project 'focus-android'.
```
(@pocmo ?) | 1.0 | Code Quality task failing: unable to find pmd - I'm not sure how long this has been a problem, but I am trying to find out why UI tests are not being ran on Firebase currently (with whatever currently pass, that's another problem), but the Code Quality task is a dependency for the scheduled UI test task.
Code Quality Failure: https://firefox-ci-tc.services.mozilla.com/tasks/OohJuDmMT-iQ9rYdBo99NA/runs/0/logs/https%3A%2F%2Ffirefox-ci-tc.services.mozilla.com%2Fapi%2Fqueue%2Fv1%2Ftask%2FOohJuDmMT-iQ9rYdBo99NA%2Fruns%2F0%2Fartifacts%2Fpublic%2Flogs%2Flive.log
```Log
<======-------> 50% CONFIGURING [37s]> :app<=============> 100% CONFIGURING [37s]
FAILURE: Build failed with an exception.
* What went wrong:
Task 'pmd' not found in root project 'focus-android'.
```
(@pocmo ?) | non_priority | code quality task failing unable to find pmd i m not sure how long this has been a problem but i am trying to find out why ui tests are not being ran on firebase currently with whatever currently pass that s another problem but the code quality task is a dependency for the scheduled ui test task code quality failure log configuring app configuring failure build failed with an exception what went wrong task pmd not found in root project focus android pocmo | 0 |
283,684 | 30,913,524,145 | IssuesEvent | 2023-08-05 02:08:05 | hshivhare67/kernel_v4.19.72 | https://api.github.com/repos/hshivhare67/kernel_v4.19.72 | reopened | CVE-2020-29370 (High) detected in linuxlinux-4.19.282 | Mend: dependency security vulnerability | ## CVE-2020-29370 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.282</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/hshivhare67/kernel_v4.19.72/commit/139c4e073703974ca0b05255c4cff6dcd52a8e31">139c4e073703974ca0b05255c4cff6dcd52a8e31</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/slub.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/slub.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in kmem_cache_alloc_bulk in mm/slub.c in the Linux kernel before 5.5.11. The slowpath lacks the required TID increment, aka CID-fd4d9c7d0c71.
<p>Publish Date: 2020-11-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-29370>CVE-2020-29370</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-29370">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-29370</a></p>
<p>Release Date: 2020-11-28</p>
<p>Fix Resolution: v5.6-rc7,v5.5.11,v5.4.28</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-29370 (High) detected in linuxlinux-4.19.282 - ## CVE-2020-29370 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.282</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/hshivhare67/kernel_v4.19.72/commit/139c4e073703974ca0b05255c4cff6dcd52a8e31">139c4e073703974ca0b05255c4cff6dcd52a8e31</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/slub.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/slub.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in kmem_cache_alloc_bulk in mm/slub.c in the Linux kernel before 5.5.11. The slowpath lacks the required TID increment, aka CID-fd4d9c7d0c71.
<p>Publish Date: 2020-11-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-29370>CVE-2020-29370</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-29370">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-29370</a></p>
<p>Release Date: 2020-11-28</p>
<p>Fix Resolution: v5.6-rc7,v5.5.11,v5.4.28</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linuxlinux cve high severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch master vulnerable source files mm slub c mm slub c vulnerability details an issue was discovered in kmem cache alloc bulk in mm slub c in the linux kernel before the slowpath lacks the required tid increment aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
1,672 | 10,566,881,060 | IssuesEvent | 2019-10-05 22:13:43 | nf-core/tools | https://api.github.com/repos/nf-core/tools | closed | TEMPLATE branch should be set up by the create command | automation | Currently the create command makes sure that the `TEMPLATE` branch is possible to create in an easy way. I think we should take it a step further and the very least recommend the user to create it and push it to github.
Related to #88.
| 1.0 | TEMPLATE branch should be set up by the create command - Currently the create command makes sure that the `TEMPLATE` branch is possible to create in an easy way. I think we should take it a step further and the very least recommend the user to create it and push it to github.
Related to #88.
| non_priority | template branch should be set up by the create command currently the create command makes sure that the template branch is possible to create in an easy way i think we should take it a step further and the very least recommend the user to create it and push it to github related to | 0 |
114,116 | 11,837,936,616 | IssuesEvent | 2020-03-23 14:55:41 | usabilla/usabilla-u4a-android-sdk | https://api.github.com/repos/usabilla/usabilla-u4a-android-sdk | closed | Support vector drawable for stars | documentation enhancement | When I set star and starOutline in UbImages as vector drawable I got crash
` java.lang.NullPointerException: Attempt to invoke virtual method 'int android.graphics.Bitmap.getWidth()' on a null object reference
at android.graphics.Bitmap.createScaledBitmap(Bitmap.java:596)
at com.usabilla.sdk.ubform.sdk.form.model.UbInternalTheme.setCustomRatingBarDrawable(UbInternalTheme.kt:79)
at com.usabilla.sdk.ubform.sdk.form.model.UbInternalTheme.getCustomRatingBarDrawable(UbInternalTheme.kt:49)
at com.usabilla.sdk.ubform.sdk.field.view.StarView.setStarsColor(StarView.kt:41)
at com.usabilla.sdk.ubform.sdk.field.view.StarView.buildSpecialisedView(StarView.kt:27)
at com.usabilla.sdk.ubform.sdk.field.presenter.common.FieldPresenter.populateView(FieldPresenter.java:46)
at com.usabilla.sdk.ubform.sdk.field.view.common.FieldView.onAttachedToWindow(FieldView.kt:97)
at android.view.View.dispatchAttachedToWindow(View.java:13406)
at android.view.ViewGroup.dispatchAttachedToWindow(ViewGroup.java:2707)
at android.view.ViewGroup.dispatchAttachedToWindow(ViewGroup.java:2714)
at android.view.ViewGroup.dispatchAttachedToWindow(ViewGroup.java:2714)
at android.view.ViewGroup.dispatchAttachedToWindow(ViewGroup.java:2714)
at android.view.ViewGroup.addViewInner(ViewGroup.java:3919)
at android.view.ViewGroup.addView(ViewGroup.java:3733)
at android.view.ViewGroup.addView(ViewGroup.java:3678)
at android.view.ViewGroup.addView(ViewGroup.java:3654)
at com.usabilla.sdk.ubform.sdk.banner.BannerFragment.onResume(BannerFragment.kt:80)
at androidx.fragment.app.Fragment.performResume(Fragment.java:2747)
at androidx.fragment.app.FragmentStateManager.resume(FragmentStateManager.java:373)
at androidx.fragment.app.FragmentManager.moveToState(FragmentManager.java:1199)
at androidx.fragment.app.FragmentManager.moveToState(FragmentManager.java:1356)
at androidx.fragment.app.FragmentManager.moveFragmentToExpectedState(FragmentManager.java:1434)
at androidx.fragment.app.FragmentManager.moveToState(FragmentManager.java:1497)
at androidx.fragment.app.BackStackRecord.executeOps(BackStackRecord.java:447)
at androidx.fragment.app.FragmentManager.executeOps(FragmentManager.java:2169)
at androidx.fragment.app.FragmentManager.executeOpsTogether(FragmentManager.java:1992)
at androidx.fragment.app.FragmentManager.removeRedundantOperationsAndExecute(FragmentManager.java:1947)
at androidx.fragment.app.FragmentManager.execPendingActions(FragmentManager.java:1849)
at androidx.fragment.app.FragmentManager$4.run(FragmentManager.java:413)
at android.os.Handler.handleCallback(Handler.java:739)
at android.os.Handler.dispatchMessage(Handler.java:95)
at android.os.Looper.loop(Looper.java:135)
at android.app.ActivityThread.main(ActivityThread.java:5221)
at java.lang.reflect.Method.invoke(Native Method)
at java.lang.reflect.Method.invoke(Method.java:372)
at com.android.internal.os.ZygoteInit$MethodAndArgsCaller.run(ZygoteInit.java:899)
at com.android.internal.os.ZygoteInit.main(ZygoteInit.java:694)` | 1.0 | Support vector drawable for stars - When I set star and starOutline in UbImages as vector drawable I got crash
` java.lang.NullPointerException: Attempt to invoke virtual method 'int android.graphics.Bitmap.getWidth()' on a null object reference
at android.graphics.Bitmap.createScaledBitmap(Bitmap.java:596)
at com.usabilla.sdk.ubform.sdk.form.model.UbInternalTheme.setCustomRatingBarDrawable(UbInternalTheme.kt:79)
at com.usabilla.sdk.ubform.sdk.form.model.UbInternalTheme.getCustomRatingBarDrawable(UbInternalTheme.kt:49)
at com.usabilla.sdk.ubform.sdk.field.view.StarView.setStarsColor(StarView.kt:41)
at com.usabilla.sdk.ubform.sdk.field.view.StarView.buildSpecialisedView(StarView.kt:27)
at com.usabilla.sdk.ubform.sdk.field.presenter.common.FieldPresenter.populateView(FieldPresenter.java:46)
at com.usabilla.sdk.ubform.sdk.field.view.common.FieldView.onAttachedToWindow(FieldView.kt:97)
at android.view.View.dispatchAttachedToWindow(View.java:13406)
at android.view.ViewGroup.dispatchAttachedToWindow(ViewGroup.java:2707)
at android.view.ViewGroup.dispatchAttachedToWindow(ViewGroup.java:2714)
at android.view.ViewGroup.dispatchAttachedToWindow(ViewGroup.java:2714)
at android.view.ViewGroup.dispatchAttachedToWindow(ViewGroup.java:2714)
at android.view.ViewGroup.addViewInner(ViewGroup.java:3919)
at android.view.ViewGroup.addView(ViewGroup.java:3733)
at android.view.ViewGroup.addView(ViewGroup.java:3678)
at android.view.ViewGroup.addView(ViewGroup.java:3654)
at com.usabilla.sdk.ubform.sdk.banner.BannerFragment.onResume(BannerFragment.kt:80)
at androidx.fragment.app.Fragment.performResume(Fragment.java:2747)
at androidx.fragment.app.FragmentStateManager.resume(FragmentStateManager.java:373)
at androidx.fragment.app.FragmentManager.moveToState(FragmentManager.java:1199)
at androidx.fragment.app.FragmentManager.moveToState(FragmentManager.java:1356)
at androidx.fragment.app.FragmentManager.moveFragmentToExpectedState(FragmentManager.java:1434)
at androidx.fragment.app.FragmentManager.moveToState(FragmentManager.java:1497)
at androidx.fragment.app.BackStackRecord.executeOps(BackStackRecord.java:447)
at androidx.fragment.app.FragmentManager.executeOps(FragmentManager.java:2169)
at androidx.fragment.app.FragmentManager.executeOpsTogether(FragmentManager.java:1992)
at androidx.fragment.app.FragmentManager.removeRedundantOperationsAndExecute(FragmentManager.java:1947)
at androidx.fragment.app.FragmentManager.execPendingActions(FragmentManager.java:1849)
at androidx.fragment.app.FragmentManager$4.run(FragmentManager.java:413)
at android.os.Handler.handleCallback(Handler.java:739)
at android.os.Handler.dispatchMessage(Handler.java:95)
at android.os.Looper.loop(Looper.java:135)
at android.app.ActivityThread.main(ActivityThread.java:5221)
at java.lang.reflect.Method.invoke(Native Method)
at java.lang.reflect.Method.invoke(Method.java:372)
at com.android.internal.os.ZygoteInit$MethodAndArgsCaller.run(ZygoteInit.java:899)
at com.android.internal.os.ZygoteInit.main(ZygoteInit.java:694)` | non_priority | support vector drawable for stars when i set star and staroutline in ubimages as vector drawable i got crash java lang nullpointerexception attempt to invoke virtual method int android graphics bitmap getwidth on a null object reference at android graphics bitmap createscaledbitmap bitmap java at com usabilla sdk ubform sdk form model ubinternaltheme setcustomratingbardrawable ubinternaltheme kt at com usabilla sdk ubform sdk form model ubinternaltheme getcustomratingbardrawable ubinternaltheme kt at com usabilla sdk ubform sdk field view starview setstarscolor starview kt at com usabilla sdk ubform sdk field view starview buildspecialisedview starview kt at com usabilla sdk ubform sdk field presenter common fieldpresenter populateview fieldpresenter java at com usabilla sdk ubform sdk field view common fieldview onattachedtowindow fieldview kt at android view view dispatchattachedtowindow view java at android view viewgroup dispatchattachedtowindow viewgroup java at android view viewgroup dispatchattachedtowindow viewgroup java at android view viewgroup dispatchattachedtowindow viewgroup java at android view viewgroup dispatchattachedtowindow viewgroup java at android view viewgroup addviewinner viewgroup java at android view viewgroup addview viewgroup java at android view viewgroup addview viewgroup java at android view viewgroup addview viewgroup java at com usabilla sdk ubform sdk banner bannerfragment onresume bannerfragment kt at androidx fragment app fragment performresume fragment java at androidx fragment app fragmentstatemanager resume fragmentstatemanager java at androidx fragment app fragmentmanager movetostate fragmentmanager java at androidx fragment app fragmentmanager movetostate fragmentmanager java at androidx fragment app fragmentmanager movefragmenttoexpectedstate fragmentmanager java at androidx fragment app fragmentmanager movetostate fragmentmanager java at androidx fragment app backstackrecord executeops backstackrecord java at androidx fragment app fragmentmanager executeops fragmentmanager java at androidx fragment app fragmentmanager executeopstogether fragmentmanager java at androidx fragment app fragmentmanager removeredundantoperationsandexecute fragmentmanager java at androidx fragment app fragmentmanager execpendingactions fragmentmanager java at androidx fragment app fragmentmanager run fragmentmanager java at android os handler handlecallback handler java at android os handler dispatchmessage handler java at android os looper loop looper java at android app activitythread main activitythread java at java lang reflect method invoke native method at java lang reflect method invoke method java at com android internal os zygoteinit methodandargscaller run zygoteinit java at com android internal os zygoteinit main zygoteinit java | 0 |
4,380 | 22,291,103,265 | IssuesEvent | 2022-06-12 11:28:02 | Lissy93/dashy | https://api.github.com/repos/Lissy93/dashy | closed | FontAwesome Icons[QUESTION] <title> | 🤷♂️ Question 👤 Awaiting Maintainer Response | ### Question
I am trying to use free "font awesome" icons but are not rendering. For example, "fa-solid fa-font-awesome"
Categories like fa-solid, fa-brands etc are not rendering but fas, fab etc are working.
### Category
Using Icons
### Please tick the boxes
- [X] You are using a [supported](https://github.com/Lissy93/dashy/blob/master/.github/SECURITY.md#supported-versions) version of Dashy (check the first two digits of the version number)
- [X] You've checked that this [question hasn't already been raised](https://github.com/Lissy93/dashy/issues?q=is%3Aissue)
- [X] You've checked the [docs](https://github.com/Lissy93/dashy/tree/master/docs#readme) and [troubleshooting](https://github.com/Lissy93/dashy/blob/master/docs/troubleshooting.md#troubleshooting) guide
- [X] You agree to the [code of conduct](https://github.com/Lissy93/dashy/blob/master/.github/CODE_OF_CONDUCT.md#contributor-covenant-code-of-conduct) | True | FontAwesome Icons[QUESTION] <title> - ### Question
I am trying to use free "font awesome" icons but are not rendering. For example, "fa-solid fa-font-awesome"
Categories like fa-solid, fa-brands etc are not rendering but fas, fab etc are working.
### Category
Using Icons
### Please tick the boxes
- [X] You are using a [supported](https://github.com/Lissy93/dashy/blob/master/.github/SECURITY.md#supported-versions) version of Dashy (check the first two digits of the version number)
- [X] You've checked that this [question hasn't already been raised](https://github.com/Lissy93/dashy/issues?q=is%3Aissue)
- [X] You've checked the [docs](https://github.com/Lissy93/dashy/tree/master/docs#readme) and [troubleshooting](https://github.com/Lissy93/dashy/blob/master/docs/troubleshooting.md#troubleshooting) guide
- [X] You agree to the [code of conduct](https://github.com/Lissy93/dashy/blob/master/.github/CODE_OF_CONDUCT.md#contributor-covenant-code-of-conduct) | non_priority | fontawesome icons question i am trying to use free font awesome icons but are not rendering for example fa solid fa font awesome categories like fa solid fa brands etc are not rendering but fas fab etc are working category using icons please tick the boxes you are using a version of dashy check the first two digits of the version number you ve checked that this you ve checked the and guide you agree to the | 0 |
68,821 | 29,581,369,565 | IssuesEvent | 2023-06-07 06:08:57 | elastic/integrations | https://api.github.com/repos/elastic/integrations | closed | Make IBMMQ GA | Team:Service-Integrations | ### Integration release checklist
This checklist is intended for integrations maintainers to ensure consistency
when creating or updating a Package, Module or Dataset for an Integration.
- [x] Change follows [development guidelines](https://github.com/elastic/integrations/tree/master/doc/development/guidelines)
- [x] Supported versions of the monitoring target are documented
- [x] Supported operating systems are documented (if applicable)
- [x] Integration or [System tests](https://github.com/elastic/elastic-package/blob/master/docs/howto/system_testing.md) exist
- [x] Documentation exists
- [x] Fields follow [ECS](https://github.com/elastic/ecs) and [naming conventions](https://www.elastic.co/guide/en/beats/devguide/master/event-conventions.html)
- [x] At least a manual test with ES / Kibana / Agent has been performed.
### Checklist
| Integration | Alpha / Beta Release Duration | Documentation | Move To GA |
|---------------|-----------------|-----------------|-------------|
| IBM MQ | 10M | Verified | :green_heart:
| Data streams | Alpha / Beta Release | Automated Tests | Simulated / Live | Manual Testing | Move To GA |
|---------------|-----------------|----------------------|-----------------|-----------------|-------------|
| errorlog| 10M | Yes | Live | done | :green_heart:
| qmgr| 9M | Yes | Live | done | :green_heart:
### Discussions:
- `Metricbeat of IBMMQ` is in beta and we are not considering metricbeat to be moved to GA as the metrics collected from integrations uses `Prometheus`.
- The enhancement requests on metricbeat is not considered when making IBMMQ GA.
### Enhancement Requests:
https://github.com/elastic/enhancements/issues/18669 - Currently we collect metrics using Prometheus HTTP endpoints. The request is to collect metrics using other option using Go Clients. | 1.0 | Make IBMMQ GA - ### Integration release checklist
This checklist is intended for integrations maintainers to ensure consistency
when creating or updating a Package, Module or Dataset for an Integration.
- [x] Change follows [development guidelines](https://github.com/elastic/integrations/tree/master/doc/development/guidelines)
- [x] Supported versions of the monitoring target are documented
- [x] Supported operating systems are documented (if applicable)
- [x] Integration or [System tests](https://github.com/elastic/elastic-package/blob/master/docs/howto/system_testing.md) exist
- [x] Documentation exists
- [x] Fields follow [ECS](https://github.com/elastic/ecs) and [naming conventions](https://www.elastic.co/guide/en/beats/devguide/master/event-conventions.html)
- [x] At least a manual test with ES / Kibana / Agent has been performed.
### Checklist
| Integration | Alpha / Beta Release Duration | Documentation | Move To GA |
|---------------|-----------------|-----------------|-------------|
| IBM MQ | 10M | Verified | :green_heart:
| Data streams | Alpha / Beta Release | Automated Tests | Simulated / Live | Manual Testing | Move To GA |
|---------------|-----------------|----------------------|-----------------|-----------------|-------------|
| errorlog| 10M | Yes | Live | done | :green_heart:
| qmgr| 9M | Yes | Live | done | :green_heart:
### Discussions:
- `Metricbeat of IBMMQ` is in beta and we are not considering metricbeat to be moved to GA as the metrics collected from integrations uses `Prometheus`.
- The enhancement requests on metricbeat is not considered when making IBMMQ GA.
### Enhancement Requests:
https://github.com/elastic/enhancements/issues/18669 - Currently we collect metrics using Prometheus HTTP endpoints. The request is to collect metrics using other option using Go Clients. | non_priority | make ibmmq ga integration release checklist this checklist is intended for integrations maintainers to ensure consistency when creating or updating a package module or dataset for an integration change follows supported versions of the monitoring target are documented supported operating systems are documented if applicable integration or exist documentation exists fields follow and at least a manual test with es kibana agent has been performed checklist integration alpha beta release duration documentation move to ga ibm mq verified green heart data streams alpha beta release automated tests simulated live manual testing move to ga errorlog yes live done green heart qmgr yes live done green heart discussions metricbeat of ibmmq is in beta and we are not considering metricbeat to be moved to ga as the metrics collected from integrations uses prometheus the enhancement requests on metricbeat is not considered when making ibmmq ga enhancement requests currently we collect metrics using prometheus http endpoints the request is to collect metrics using other option using go clients | 0 |
102,822 | 12,825,712,905 | IssuesEvent | 2020-07-06 15:22:25 | Ferlab-Ste-Justine/clin-project | https://api.github.com/repos/Ferlab-Ste-Justine/clin-project | closed | Rajouter d'autres colonnes pour liste des patients | Clin Clin Design Front-end |

Ajouter dans l’option “Afficher” les colonnes suivantes:
- MRN
- RAMQ, ID Famille
- Famille
- ID Specimen
- Étude
**Ces colonnes seront décochées par defaut**
| 1.0 | Rajouter d'autres colonnes pour liste des patients -

Ajouter dans l’option “Afficher” les colonnes suivantes:
- MRN
- RAMQ, ID Famille
- Famille
- ID Specimen
- Étude
**Ces colonnes seront décochées par defaut**
| non_priority | rajouter d autres colonnes pour liste des patients ajouter dans l’option “afficher” les colonnes suivantes mrn ramq id famille famille id specimen étude ces colonnes seront décochées par defaut | 0 |
108,630 | 11,597,131,154 | IssuesEvent | 2020-02-24 20:14:35 | AbsaOSS/ohmyglb | https://api.github.com/repos/AbsaOSS/ohmyglb | opened | Release preparation | documentation enhancement | In preparation for the `1.0` release, complete the following items:
* API stabilisation
* Add full documentation
* Publish to [OperatorHub](https://operatorhub.io/)
All documentation and publishing items above should have the corresponding infrastructure/pipelines implemented for automated publishing etc. | 1.0 | Release preparation - In preparation for the `1.0` release, complete the following items:
* API stabilisation
* Add full documentation
* Publish to [OperatorHub](https://operatorhub.io/)
All documentation and publishing items above should have the corresponding infrastructure/pipelines implemented for automated publishing etc. | non_priority | release preparation in preparation for the release complete the following items api stabilisation add full documentation publish to all documentation and publishing items above should have the corresponding infrastructure pipelines implemented for automated publishing etc | 0 |
308,983 | 23,278,119,232 | IssuesEvent | 2022-08-05 09:15:54 | freqtrade/freqtrade | https://api.github.com/repos/freqtrade/freqtrade | closed | The documentation on "config collision handling" text is misleading. It shows 2 different expectations. | Documentation | ## Describe your environment
* Operating system: Ubuntu 20.04
* Python Version: Python 3.8.10
* CCXT version: ccxt==1.90.47
* Freqtrade Version: freqtrade 2022.6
## Describe the problem:
The documentation on "config collision handling" text is misleading. It shows 2 different expectations.
### Steps to reproduce:
Go to location: https://www.freqtrade.io/en/stable/configuration/ -> "config collision handling"
### Observed Results:
It says:
user_data/config.json -> "max_open_trades": 3,
user_data/config-import.json -> "max_open_trades": 10,
=> combined = "max_open_trades": 10,"
But in the text: "max_open_trades would be 3 after the merging"
So it's not clear if it's 3 or 10. | 1.0 | The documentation on "config collision handling" text is misleading. It shows 2 different expectations. - ## Describe your environment
* Operating system: Ubuntu 20.04
* Python Version: Python 3.8.10
* CCXT version: ccxt==1.90.47
* Freqtrade Version: freqtrade 2022.6
## Describe the problem:
The documentation on "config collision handling" text is misleading. It shows 2 different expectations.
### Steps to reproduce:
Go to location: https://www.freqtrade.io/en/stable/configuration/ -> "config collision handling"
### Observed Results:
It says:
user_data/config.json -> "max_open_trades": 3,
user_data/config-import.json -> "max_open_trades": 10,
=> combined = "max_open_trades": 10,"
But in the text: "max_open_trades would be 3 after the merging"
So it's not clear if it's 3 or 10. | non_priority | the documentation on config collision handling text is misleading it shows different expectations describe your environment operating system ubuntu python version python ccxt version ccxt freqtrade version freqtrade describe the problem the documentation on config collision handling text is misleading it shows different expectations steps to reproduce go to location config collision handling observed results it says user data config json max open trades user data config import json max open trades combined max open trades but in the text max open trades would be after the merging so it s not clear if it s or | 0 |
261,509 | 22,747,830,049 | IssuesEvent | 2022-07-07 10:44:04 | mozilla-mobile/fenix | https://api.github.com/repos/mozilla-mobile/fenix | closed | Intermittent UI test failure - < SmokeTest. mainMenuOpenInAppTest > | b:crash eng:intermittent-test eng:ui-test | ### Firebase Test Run: [Firebase link](https://console.firebase.google.com/u/0/project/moz-fenix/testlab/histories/bh.66b7091e15d53d45/matrices/7855219871393933100/executions/bs.346340389212444/testcases/1/test-cases)
### Stacktrace:
05-02 18:42:25.596: I/WindowManager(478): Input event dispatching timed out sending to org.mozilla.fenix.debug/org.mozilla.fenix.HomeActivity. Reason: f3c44e7 org.mozilla.fenix.debug/org.mozilla.fenix.HomeActivity (server) is not responding. Waited 5001ms for FocusEvent(hasFocus=false)
05-02 18:42:25.766: W/system_server(478): Long monitor contention with owner InputDispatcher (1484) at long com.android.server.wm.InputManagerCallback.notifyANRInner(android.view.InputApplicationHandle, android.os.IBinder, java.lang.String)(InputManagerCallback.java:249) waiters=0 in boolean com.android.server.wm.WindowProcessController.hasActivitiesOrRecentTasks() for 142ms
05-02 18:42:25.766: W/ActivityManager(478): Slow operation: 144ms so far, now at getContentProviderImpl: after updateLruProcess
05-02 18:42:25.766: W/ActivityManager(478): Slow operation: 144ms so far, now at getContentProviderImpl: before updateOomAdj
05-02 18:42:25.768: W/ActivityManager(478): Slow operation: 145ms so far, now at getContentProviderImpl: after updateOomAdj
05-02 18:42:25.768: W/ActivityManager(478): Slow operation: 145ms so far, now at getContentProviderImpl: done!
05-02 18:42:25.793: I/ActivityManager(478): Force stopping org.mozilla.fenix.debug appid=10151 user=0: finished inst
05-02 18:42:25.794: I/ActivityManager(478): Killing 11948:org.mozilla.fenix.debug/u0a151 (adj 0): stop org.mozilla.fenix.debug due to finished inst
05-02 18:42:25.795: W/ActivityTaskManager(478): Force removing ActivityRecord{786a462 u0 org.mozilla.fenix.debug/org.mozilla.fenix.HomeActivity t9 f}}: app died, no saved state
05-02 18:42:25.798: W/Binder(11923): Caught a RuntimeException from the binder stub implementation.
05-02 18:42:25.798: W/Binder(11923): java.lang.SecurityException: Calling from not trusted UID!
05-02 18:42:25.798: W/Binder(11923): at android.app.UiAutomationConnection.throwIfCalledByNotTrustedUidLocked(UiAutomationConnection.java:525)
05-02 18:42:25.798: W/Binder(11923): at android.app.UiAutomationConnection.shutdown(UiAutomationConnection.java:429)
05-02 18:42:25.798: W/Binder(11923): at android.app.IUiAutomationConnection$Stub.onTransact(IUiAutomationConnection.java:390)
05-02 18:42:25.798: W/Binder(11923): at android.os.Binder.execTransactInternal(Binder.java:1159)
05-02 18:42:25.798: W/Binder(11923): at android.os.Binder.execTransact(Binder.java:1123)
05-02 18:42:25.800: I/ServiceChildProcess(12633): Destroying GeckoServiceChildProcess
05-02 18:42:25.802: I/ServiceChildProcess(12801): Destroying GeckoServiceChildProcess
05-02 18:42:25.807: I/ActivityManager(478): Killing 12633:org.mozilla.fenix.debug:tab4/u0a151 (adj 0): stop org.mozilla.fenix.debug due to finished inst
05-02 18:42:25.808: I/ActivityManager(478): Killing 12801:org.mozilla.fenix.debug:gpu/u0a151 (adj 0): stop org.mozilla.fenix.debug due to finished inst
05-02 18:42:25.810: D/WindowManager(478): notifyANR took 217ms
### Build: 5/3 Main
### Notes Similar with #24047
┆Issue is synchronized with this [Jira Task](https://mozilla-hub.atlassian.net/browse/FNXV2-20353)
| 2.0 | Intermittent UI test failure - < SmokeTest. mainMenuOpenInAppTest > - ### Firebase Test Run: [Firebase link](https://console.firebase.google.com/u/0/project/moz-fenix/testlab/histories/bh.66b7091e15d53d45/matrices/7855219871393933100/executions/bs.346340389212444/testcases/1/test-cases)
### Stacktrace:
05-02 18:42:25.596: I/WindowManager(478): Input event dispatching timed out sending to org.mozilla.fenix.debug/org.mozilla.fenix.HomeActivity. Reason: f3c44e7 org.mozilla.fenix.debug/org.mozilla.fenix.HomeActivity (server) is not responding. Waited 5001ms for FocusEvent(hasFocus=false)
05-02 18:42:25.766: W/system_server(478): Long monitor contention with owner InputDispatcher (1484) at long com.android.server.wm.InputManagerCallback.notifyANRInner(android.view.InputApplicationHandle, android.os.IBinder, java.lang.String)(InputManagerCallback.java:249) waiters=0 in boolean com.android.server.wm.WindowProcessController.hasActivitiesOrRecentTasks() for 142ms
05-02 18:42:25.766: W/ActivityManager(478): Slow operation: 144ms so far, now at getContentProviderImpl: after updateLruProcess
05-02 18:42:25.766: W/ActivityManager(478): Slow operation: 144ms so far, now at getContentProviderImpl: before updateOomAdj
05-02 18:42:25.768: W/ActivityManager(478): Slow operation: 145ms so far, now at getContentProviderImpl: after updateOomAdj
05-02 18:42:25.768: W/ActivityManager(478): Slow operation: 145ms so far, now at getContentProviderImpl: done!
05-02 18:42:25.793: I/ActivityManager(478): Force stopping org.mozilla.fenix.debug appid=10151 user=0: finished inst
05-02 18:42:25.794: I/ActivityManager(478): Killing 11948:org.mozilla.fenix.debug/u0a151 (adj 0): stop org.mozilla.fenix.debug due to finished inst
05-02 18:42:25.795: W/ActivityTaskManager(478): Force removing ActivityRecord{786a462 u0 org.mozilla.fenix.debug/org.mozilla.fenix.HomeActivity t9 f}}: app died, no saved state
05-02 18:42:25.798: W/Binder(11923): Caught a RuntimeException from the binder stub implementation.
05-02 18:42:25.798: W/Binder(11923): java.lang.SecurityException: Calling from not trusted UID!
05-02 18:42:25.798: W/Binder(11923): at android.app.UiAutomationConnection.throwIfCalledByNotTrustedUidLocked(UiAutomationConnection.java:525)
05-02 18:42:25.798: W/Binder(11923): at android.app.UiAutomationConnection.shutdown(UiAutomationConnection.java:429)
05-02 18:42:25.798: W/Binder(11923): at android.app.IUiAutomationConnection$Stub.onTransact(IUiAutomationConnection.java:390)
05-02 18:42:25.798: W/Binder(11923): at android.os.Binder.execTransactInternal(Binder.java:1159)
05-02 18:42:25.798: W/Binder(11923): at android.os.Binder.execTransact(Binder.java:1123)
05-02 18:42:25.800: I/ServiceChildProcess(12633): Destroying GeckoServiceChildProcess
05-02 18:42:25.802: I/ServiceChildProcess(12801): Destroying GeckoServiceChildProcess
05-02 18:42:25.807: I/ActivityManager(478): Killing 12633:org.mozilla.fenix.debug:tab4/u0a151 (adj 0): stop org.mozilla.fenix.debug due to finished inst
05-02 18:42:25.808: I/ActivityManager(478): Killing 12801:org.mozilla.fenix.debug:gpu/u0a151 (adj 0): stop org.mozilla.fenix.debug due to finished inst
05-02 18:42:25.810: D/WindowManager(478): notifyANR took 217ms
### Build: 5/3 Main
### Notes Similar with #24047
┆Issue is synchronized with this [Jira Task](https://mozilla-hub.atlassian.net/browse/FNXV2-20353)
| non_priority | intermittent ui test failure firebase test run stacktrace i windowmanager input event dispatching timed out sending to org mozilla fenix debug org mozilla fenix homeactivity reason org mozilla fenix debug org mozilla fenix homeactivity server is not responding waited for focusevent hasfocus false w system server long monitor contention with owner inputdispatcher at long com android server wm inputmanagercallback notifyanrinner android view inputapplicationhandle android os ibinder java lang string inputmanagercallback java waiters in boolean com android server wm windowprocesscontroller hasactivitiesorrecenttasks for w activitymanager slow operation so far now at getcontentproviderimpl after updatelruprocess w activitymanager slow operation so far now at getcontentproviderimpl before updateoomadj w activitymanager slow operation so far now at getcontentproviderimpl after updateoomadj w activitymanager slow operation so far now at getcontentproviderimpl done i activitymanager force stopping org mozilla fenix debug appid user finished inst i activitymanager killing org mozilla fenix debug adj stop org mozilla fenix debug due to finished inst w activitytaskmanager force removing activityrecord org mozilla fenix debug org mozilla fenix homeactivity f app died no saved state w binder caught a runtimeexception from the binder stub implementation w binder java lang securityexception calling from not trusted uid w binder at android app uiautomationconnection throwifcalledbynottrusteduidlocked uiautomationconnection java w binder at android app uiautomationconnection shutdown uiautomationconnection java w binder at android app iuiautomationconnection stub ontransact iuiautomationconnection java w binder at android os binder exectransactinternal binder java w binder at android os binder exectransact binder java i servicechildprocess destroying geckoservicechildprocess i servicechildprocess destroying geckoservicechildprocess i activitymanager killing org mozilla fenix debug adj stop org mozilla fenix debug due to finished inst i activitymanager killing org mozilla fenix debug gpu adj stop org mozilla fenix debug due to finished inst d windowmanager notifyanr took build main notes similar with ┆issue is synchronized with this | 0 |
108,215 | 23,579,389,881 | IssuesEvent | 2022-08-23 06:06:56 | sast-automation-dev/easybuggy4kt-11 | https://api.github.com/repos/sast-automation-dev/easybuggy4kt-11 | opened | Code Security Report: 19 high severity findings, 38 total findings | code security findings | # Code Security Report
**Latest Scan:** 2022-08-23 06:06am
**Total Findings:** 38
**Tested Project Files:** 99
**Detected Programming Languages:** 2
<!-- SAST-MANUAL-SCAN-START -->
- [ ] Check this box to manually trigger a scan
<!-- SAST-MANUAL-SCAN-END -->
## Language: Java
> No vulnerability findings detected.
## Language: Kotlin
| Severity | CWE | Vulnerability Type | Count |
|-|-|-|-|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-79](https://cwe.mitre.org/data/definitions/79.html)|Cross-Site Scripting|19|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-338](https://cwe.mitre.org/data/definitions/338.html)|Weak Pseudo-Random|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-244](https://cwe.mitre.org/data/definitions/244.html)|Heap Inspection|7|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-501](https://cwe.mitre.org/data/definitions/501.html)|Trust Boundary Violation|4|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-434](https://cwe.mitre.org/data/definitions/434.html)|File Upload|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-601](https://cwe.mitre.org/data/definitions/601.html)|Unvalidated/Open Redirect|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-117](https://cwe.mitre.org/data/definitions/117.html)|Log Forging|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-113](https://cwe.mitre.org/data/definitions/113.html)|HTTP Header Injection|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-20](https://cwe.mitre.org/data/definitions/20.html)|Mail Relay|3|
### Details
> The below list presents the 19 high vulnerability findings that need your attention. To view information on these findings, navigate to the [Mend SAST Application](https://dev.whitesourcesoftware.com/sast/#/scans/788b78ae-893a-45a3-9f00-4411b746ddeb/details).
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20>Cross-Site Scripting (CWE-79) : 19</summary>
#### Findings
<details>
<summary>vulnerabilities/XEEandXXEController.kt:47</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/XEEandXXEController.kt#L42-L47
</details>
<details>
<summary>vulnerabilities/OGNLExpressionInjectionController.kt:42</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/OGNLExpressionInjectionController.kt#L37-L42
</details>
<details>
<summary>vulnerabilities/XSSController.kt:22</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/XSSController.kt#L17-L22
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/XSSController.kt#L21
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/XSSController.kt#L22
</details>
</details>
<details>
<summary>vulnerabilities/XEEandXXEController.kt:53</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/XEEandXXEController.kt#L48-L53
</details>
<details>
<summary>performance/CreatingUnnecessaryObjectsController.kt:44</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L39-L44
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L17
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L41
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L44
</details>
</details>
<details>
<summary>performance/CreatingUnnecessaryObjectsController.kt:44</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L39-L44
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L17
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L32
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L44
</details>
</details>
<details>
<summary>performance/CreatingUnnecessaryObjectsController.kt:44</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L39-L44
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L17
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L31
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L44
</details>
</details>
<details>
<summary>performance/CreatingUnnecessaryObjectsController.kt:22</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L17-L22
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L17
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L22
</details>
</details>
<details>
<summary>performance/StringPlusOperationController.kt:22</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/StringPlusOperationController.kt#L17-L22
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/StringPlusOperationController.kt#L20
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/StringPlusOperationController.kt#L21
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/StringPlusOperationController.kt#L22
</details>
</details>
<details>
<summary>vulnerabilities/ClickJackingController.kt:56</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/ClickJackingController.kt#L51-L56
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/ClickJackingController.kt#L48
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/ClickJackingController.kt#L56
</details>
</details>
<details>
<summary>vulnerabilities/CSRFController.kt:59</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/CSRFController.kt#L54-L59
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/CSRFController.kt#L40
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/CSRFController.kt#L59
</details>
</details>
<details>
<summary>troubles/TruncationErrorController.kt:22</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/TruncationErrorController.kt#L17-L22
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/TruncationErrorController.kt#L19
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/TruncationErrorController.kt#L22
</details>
</details>
<details>
<summary>troubles/TruncationErrorController.kt:21</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/TruncationErrorController.kt#L16-L21
</details>
<details>
<summary>troubles/LossOfTrailingDigitsController.kt:21</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/LossOfTrailingDigitsController.kt#L16-L21
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/LossOfTrailingDigitsController.kt#L18
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/LossOfTrailingDigitsController.kt#L21
</details>
</details>
<details>
<summary>troubles/LossOfTrailingDigitsController.kt:20</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/LossOfTrailingDigitsController.kt#L15-L20
</details>
<details>
<summary>troubles/RoundOffErrorController.kt:21</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/RoundOffErrorController.kt#L16-L21
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/RoundOffErrorController.kt#L18
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/RoundOffErrorController.kt#L21
</details>
</details>
<details>
<summary>troubles/RoundOffErrorController.kt:20</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/RoundOffErrorController.kt#L15-L20
</details>
<details>
<summary>troubles/IntegerOverflowController.kt:35</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/IntegerOverflowController.kt#L30-L35
</details>
<details>
<summary>vulnerabilities/XEEandXXEController.kt:51</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/XEEandXXEController.kt#L46-L51
</details>
</details>
| 1.0 | Code Security Report: 19 high severity findings, 38 total findings - # Code Security Report
**Latest Scan:** 2022-08-23 06:06am
**Total Findings:** 38
**Tested Project Files:** 99
**Detected Programming Languages:** 2
<!-- SAST-MANUAL-SCAN-START -->
- [ ] Check this box to manually trigger a scan
<!-- SAST-MANUAL-SCAN-END -->
## Language: Java
> No vulnerability findings detected.
## Language: Kotlin
| Severity | CWE | Vulnerability Type | Count |
|-|-|-|-|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-79](https://cwe.mitre.org/data/definitions/79.html)|Cross-Site Scripting|19|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-338](https://cwe.mitre.org/data/definitions/338.html)|Weak Pseudo-Random|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-244](https://cwe.mitre.org/data/definitions/244.html)|Heap Inspection|7|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-501](https://cwe.mitre.org/data/definitions/501.html)|Trust Boundary Violation|4|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-434](https://cwe.mitre.org/data/definitions/434.html)|File Upload|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-601](https://cwe.mitre.org/data/definitions/601.html)|Unvalidated/Open Redirect|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-117](https://cwe.mitre.org/data/definitions/117.html)|Log Forging|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-113](https://cwe.mitre.org/data/definitions/113.html)|HTTP Header Injection|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-20](https://cwe.mitre.org/data/definitions/20.html)|Mail Relay|3|
### Details
> The below list presents the 19 high vulnerability findings that need your attention. To view information on these findings, navigate to the [Mend SAST Application](https://dev.whitesourcesoftware.com/sast/#/scans/788b78ae-893a-45a3-9f00-4411b746ddeb/details).
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20>Cross-Site Scripting (CWE-79) : 19</summary>
#### Findings
<details>
<summary>vulnerabilities/XEEandXXEController.kt:47</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/XEEandXXEController.kt#L42-L47
</details>
<details>
<summary>vulnerabilities/OGNLExpressionInjectionController.kt:42</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/OGNLExpressionInjectionController.kt#L37-L42
</details>
<details>
<summary>vulnerabilities/XSSController.kt:22</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/XSSController.kt#L17-L22
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/XSSController.kt#L21
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/XSSController.kt#L22
</details>
</details>
<details>
<summary>vulnerabilities/XEEandXXEController.kt:53</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/XEEandXXEController.kt#L48-L53
</details>
<details>
<summary>performance/CreatingUnnecessaryObjectsController.kt:44</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L39-L44
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L17
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L41
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L44
</details>
</details>
<details>
<summary>performance/CreatingUnnecessaryObjectsController.kt:44</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L39-L44
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L17
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L32
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L44
</details>
</details>
<details>
<summary>performance/CreatingUnnecessaryObjectsController.kt:44</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L39-L44
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L17
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L31
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L44
</details>
</details>
<details>
<summary>performance/CreatingUnnecessaryObjectsController.kt:22</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L17-L22
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L17
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/CreatingUnnecessaryObjectsController.kt#L22
</details>
</details>
<details>
<summary>performance/StringPlusOperationController.kt:22</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/StringPlusOperationController.kt#L17-L22
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/StringPlusOperationController.kt#L20
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/StringPlusOperationController.kt#L21
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/performance/StringPlusOperationController.kt#L22
</details>
</details>
<details>
<summary>vulnerabilities/ClickJackingController.kt:56</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/ClickJackingController.kt#L51-L56
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/ClickJackingController.kt#L48
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/ClickJackingController.kt#L56
</details>
</details>
<details>
<summary>vulnerabilities/CSRFController.kt:59</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/CSRFController.kt#L54-L59
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/CSRFController.kt#L40
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/CSRFController.kt#L59
</details>
</details>
<details>
<summary>troubles/TruncationErrorController.kt:22</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/TruncationErrorController.kt#L17-L22
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/TruncationErrorController.kt#L19
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/TruncationErrorController.kt#L22
</details>
</details>
<details>
<summary>troubles/TruncationErrorController.kt:21</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/TruncationErrorController.kt#L16-L21
</details>
<details>
<summary>troubles/LossOfTrailingDigitsController.kt:21</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/LossOfTrailingDigitsController.kt#L16-L21
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/LossOfTrailingDigitsController.kt#L18
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/LossOfTrailingDigitsController.kt#L21
</details>
</details>
<details>
<summary>troubles/LossOfTrailingDigitsController.kt:20</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/LossOfTrailingDigitsController.kt#L15-L20
</details>
<details>
<summary>troubles/RoundOffErrorController.kt:21</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/RoundOffErrorController.kt#L16-L21
<details>
<summary> Trace </summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/RoundOffErrorController.kt#L18
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/RoundOffErrorController.kt#L21
</details>
</details>
<details>
<summary>troubles/RoundOffErrorController.kt:20</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/RoundOffErrorController.kt#L15-L20
</details>
<details>
<summary>troubles/IntegerOverflowController.kt:35</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/troubles/IntegerOverflowController.kt#L30-L35
</details>
<details>
<summary>vulnerabilities/XEEandXXEController.kt:51</summary>
https://github.com/sast-automation-dev/easybuggy4kt-11/blob/a4b6e96e2a731a952676dea649d3b01f116ee86d/easybuggy4kt-11/src/main/kotlin/org/t246osslab/easybuggy4kt/vulnerabilities/XEEandXXEController.kt#L46-L51
</details>
</details>
| non_priority | code security report high severity findings total findings code security report latest scan total findings tested project files detected programming languages check this box to manually trigger a scan language java no vulnerability findings detected language kotlin severity cwe vulnerability type count high scripting medium pseudo random medium inspection medium boundary violation low upload low redirect low forging low header injection low relay details the below list presents the high vulnerability findings that need your attention to view information on these findings navigate to the cross site scripting cwe findings vulnerabilities xeeandxxecontroller kt vulnerabilities ognlexpressioninjectioncontroller kt vulnerabilities xsscontroller kt trace vulnerabilities xeeandxxecontroller kt performance creatingunnecessaryobjectscontroller kt trace performance creatingunnecessaryobjectscontroller kt trace performance creatingunnecessaryobjectscontroller kt trace performance creatingunnecessaryobjectscontroller kt trace performance stringplusoperationcontroller kt trace vulnerabilities clickjackingcontroller kt trace vulnerabilities csrfcontroller kt trace troubles truncationerrorcontroller kt trace troubles truncationerrorcontroller kt troubles lossoftrailingdigitscontroller kt trace troubles lossoftrailingdigitscontroller kt troubles roundofferrorcontroller kt trace troubles roundofferrorcontroller kt troubles integeroverflowcontroller kt vulnerabilities xeeandxxecontroller kt | 0 |
47,393 | 7,324,702,603 | IssuesEvent | 2018-03-03 00:16:32 | dart-lang/sdk | https://api.github.com/repos/dart-lang/sdk | closed | Document "CleanupTransformer" | Resolution: assumed stale area-documentation | It took me quite a while to figure out how to delete Assets with a transformer.
I took this approach: https://goo.gl/jKiQhV
Please add a few lines of documentation how to remove!!!! Assets. - Thanks!
| 1.0 | Document "CleanupTransformer" - It took me quite a while to figure out how to delete Assets with a transformer.
I took this approach: https://goo.gl/jKiQhV
Please add a few lines of documentation how to remove!!!! Assets. - Thanks!
| non_priority | document cleanuptransformer it took me quite a while to figure out how to delete assets with a transformer i took this approach please add a few lines of documentation how to remove assets thanks | 0 |
38,238 | 19,031,032,537 | IssuesEvent | 2021-11-24 10:41:23 | opencollective/opencollective | https://api.github.com/repos/opencollective/opencollective | opened | Improve the performances of the expense form | expenses complexity → medium frontend enhancement performance | The expense form can sometimes feel unresponsive. We made it more and more complex with time, adding many fields and options, without spending much time on optimizing the form. We should have a pass on that:
- [ ] Profile updates when typing in fields, see where we spend the most time
- [ ] Use `FastField` (from formik) on the fields that are slow to re-render
- [ ] Memoize values or use pure components where necessary | True | Improve the performances of the expense form - The expense form can sometimes feel unresponsive. We made it more and more complex with time, adding many fields and options, without spending much time on optimizing the form. We should have a pass on that:
- [ ] Profile updates when typing in fields, see where we spend the most time
- [ ] Use `FastField` (from formik) on the fields that are slow to re-render
- [ ] Memoize values or use pure components where necessary | non_priority | improve the performances of the expense form the expense form can sometimes feel unresponsive we made it more and more complex with time adding many fields and options without spending much time on optimizing the form we should have a pass on that profile updates when typing in fields see where we spend the most time use fastfield from formik on the fields that are slow to re render memoize values or use pure components where necessary | 0 |
428,223 | 29,934,368,445 | IssuesEvent | 2023-06-22 11:45:43 | JanssenProject/jans | https://api.github.com/repos/JanssenProject/jans | closed | docs(config-api): rectify agama doc title | area-documentation | **Describe the bug**
Agama - Developer Studio to be renamed as `Agama`
| 1.0 | docs(config-api): rectify agama doc title - **Describe the bug**
Agama - Developer Studio to be renamed as `Agama`
| non_priority | docs config api rectify agama doc title describe the bug agama developer studio to be renamed as agama | 0 |
11,321 | 8,363,964,330 | IssuesEvent | 2018-10-03 21:14:08 | secureCodeBox/secureCodeBox | https://api.github.com/repos/secureCodeBox/secureCodeBox | opened | New Scanner: Integrate a Wordpress Scanner | new security scanner | As an user i want to use the [Wordpress Security Scanner](https://wpscan.org/) with the secureCodeBox, to test my Wordpress instance, if there are some old plugin versions installed. | True | New Scanner: Integrate a Wordpress Scanner - As an user i want to use the [Wordpress Security Scanner](https://wpscan.org/) with the secureCodeBox, to test my Wordpress instance, if there are some old plugin versions installed. | non_priority | new scanner integrate a wordpress scanner as an user i want to use the with the securecodebox to test my wordpress instance if there are some old plugin versions installed | 0 |
169,715 | 20,841,883,563 | IssuesEvent | 2022-03-21 01:45:39 | renfei/start-ui | https://api.github.com/repos/renfei/start-ui | opened | CVE-2022-0686 (High) detected in url-parse-1.5.1.tgz | security vulnerability | ## CVE-2022-0686 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.5.1.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.5.1.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.5.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- cli-service-4.5.13.tgz (Root Library)
- webpack-dev-server-3.11.2.tgz
- sockjs-client-1.5.1.tgz
- :x: **url-parse-1.5.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Authorization Bypass Through User-Controlled Key in NPM url-parse prior to 1.5.8.
<p>Publish Date: 2022-02-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0686>CVE-2022-0686</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0686">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0686</a></p>
<p>Release Date: 2022-02-20</p>
<p>Fix Resolution: url-parse - 1.5.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-0686 (High) detected in url-parse-1.5.1.tgz - ## CVE-2022-0686 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.5.1.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.5.1.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.5.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- cli-service-4.5.13.tgz (Root Library)
- webpack-dev-server-3.11.2.tgz
- sockjs-client-1.5.1.tgz
- :x: **url-parse-1.5.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Authorization Bypass Through User-Controlled Key in NPM url-parse prior to 1.5.8.
<p>Publish Date: 2022-02-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0686>CVE-2022-0686</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0686">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0686</a></p>
<p>Release Date: 2022-02-20</p>
<p>Fix Resolution: url-parse - 1.5.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in url parse tgz cve high severity vulnerability vulnerable library url parse tgz small footprint url parser that works seamlessly across node js and browser environments library home page a href path to dependency file package json path to vulnerable library node modules url parse package json dependency hierarchy cli service tgz root library webpack dev server tgz sockjs client tgz x url parse tgz vulnerable library found in base branch master vulnerability details authorization bypass through user controlled key in npm url parse prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution url parse step up your open source security game with whitesource | 0 |
207,232 | 23,435,367,951 | IssuesEvent | 2022-08-15 09:13:36 | Gal-Doron/Baragon-38 | https://api.github.com/repos/Gal-Doron/Baragon-38 | opened | jackson-dataformat-yaml-2.9.9.jar: 1 vulnerabilities (highest severity is: 7.5) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-dataformat-yaml-2.9.9.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /BaragonService/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.23/snakeyaml-1.23.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.23/snakeyaml-1.23.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.23/snakeyaml-1.23.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-38/commit/4f0aaf4c2693db4f4c37ab983c3da101d2f69d3e">4f0aaf4c2693db4f4c37ab983c3da101d2f69d3e</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2017-18640](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18640) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | snakeyaml-1.23.jar | Transitive | 2.10.4 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-18640</summary>
### Vulnerable Library - <b>snakeyaml-1.23.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.23/snakeyaml-1.23.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.23/snakeyaml-1.23.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.23/snakeyaml-1.23.jar</p>
<p>
Dependency Hierarchy:
- jackson-dataformat-yaml-2.9.9.jar (Root Library)
- :x: **snakeyaml-1.23.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-38/commit/4f0aaf4c2693db4f4c37ab983c3da101d2f69d3e">4f0aaf4c2693db4f4c37ab983c3da101d2f69d3e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Alias feature in SnakeYAML before 1.26 allows entity expansion during a load operation, a related issue to CVE-2003-1564.
<p>Publish Date: 2019-12-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18640>CVE-2017-18640</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-18640">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-18640</a></p>
<p>Release Date: 2019-12-12</p>
<p>Fix Resolution (org.yaml:snakeyaml): 1.26</p>
<p>Direct dependency fix Resolution (com.fasterxml.jackson.dataformat:jackson-dataformat-yaml): 2.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | True | jackson-dataformat-yaml-2.9.9.jar: 1 vulnerabilities (highest severity is: 7.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-dataformat-yaml-2.9.9.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /BaragonService/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.23/snakeyaml-1.23.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.23/snakeyaml-1.23.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.23/snakeyaml-1.23.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-38/commit/4f0aaf4c2693db4f4c37ab983c3da101d2f69d3e">4f0aaf4c2693db4f4c37ab983c3da101d2f69d3e</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2017-18640](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18640) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | snakeyaml-1.23.jar | Transitive | 2.10.4 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-18640</summary>
### Vulnerable Library - <b>snakeyaml-1.23.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.23/snakeyaml-1.23.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.23/snakeyaml-1.23.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.23/snakeyaml-1.23.jar</p>
<p>
Dependency Hierarchy:
- jackson-dataformat-yaml-2.9.9.jar (Root Library)
- :x: **snakeyaml-1.23.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-38/commit/4f0aaf4c2693db4f4c37ab983c3da101d2f69d3e">4f0aaf4c2693db4f4c37ab983c3da101d2f69d3e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Alias feature in SnakeYAML before 1.26 allows entity expansion during a load operation, a related issue to CVE-2003-1564.
<p>Publish Date: 2019-12-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18640>CVE-2017-18640</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-18640">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-18640</a></p>
<p>Release Date: 2019-12-12</p>
<p>Fix Resolution (org.yaml:snakeyaml): 1.26</p>
<p>Direct dependency fix Resolution (com.fasterxml.jackson.dataformat:jackson-dataformat-yaml): 2.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | non_priority | jackson dataformat yaml jar vulnerabilities highest severity is vulnerable library jackson dataformat yaml jar path to dependency file baragonservice pom xml path to vulnerable library home wss scanner repository org yaml snakeyaml snakeyaml jar home wss scanner repository org yaml snakeyaml snakeyaml jar home wss scanner repository org yaml snakeyaml snakeyaml jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high snakeyaml jar transitive details cve vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library home wss scanner repository org yaml snakeyaml snakeyaml jar home wss scanner repository org yaml snakeyaml snakeyaml jar home wss scanner repository org yaml snakeyaml snakeyaml jar dependency hierarchy jackson dataformat yaml jar root library x snakeyaml jar vulnerable library found in head commit a href found in base branch master vulnerability details the alias feature in snakeyaml before allows entity expansion during a load operation a related issue to cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml direct dependency fix resolution com fasterxml jackson dataformat jackson dataformat yaml rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue | 0 |
9,603 | 8,677,914,975 | IssuesEvent | 2018-11-30 18:13:44 | terraform-providers/terraform-provider-azurerm | https://api.github.com/repos/terraform-providers/terraform-provider-azurerm | closed | Timezone parameter missing on azurerm_recovery_services_protection_policy_vm | bug service/recovery-services | First of all, thank you for adding the resource!
As I have already posted, Azure requires the timezone to be specified, it would help alot if it can be implemented in the resource.

_Originally posted by @AndreasMWalter in https://github.com/terraform-providers/terraform-provider-azurerm/pull/1978#issuecomment-432252913_ | 2.0 | Timezone parameter missing on azurerm_recovery_services_protection_policy_vm - First of all, thank you for adding the resource!
As I have already posted, Azure requires the timezone to be specified, it would help alot if it can be implemented in the resource.

_Originally posted by @AndreasMWalter in https://github.com/terraform-providers/terraform-provider-azurerm/pull/1978#issuecomment-432252913_ | non_priority | timezone parameter missing on azurerm recovery services protection policy vm first of all thank you for adding the resource as i have already posted azure requires the timezone to be specified it would help alot if it can be implemented in the resource originally posted by andreasmwalter in | 0 |
9,673 | 8,074,058,718 | IssuesEvent | 2018-08-06 21:30:38 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | Several build issues around referencing MS.VS.Text.Internal.dll | Area-Infrastructure | - [ ] This line should have backslashes and not forward slashes: https://github.com/dotnet/roslyn/blob/08a22f8557a7eecbf1862bdcd92d25a9b1ca3b4e/build/Targets/Versions.props#L61
- [ ] 6 Test projects at EditorFeatures level use this line to reference MS.VS.Text.Internal: https://github.com/dotnet/roslyn/blob/08a22f8557a7eecbf1862bdcd92d25a9b1ca3b4e/src/EditorFeatures/VisualBasicTest/BasicEditorServicesTest.vbproj#L61-L64
- [ ] The Editor's NuGet package for MS.VS.Text.Internal has an empty ref folder - the Editor needs to fix that.
Instead of referencing the .dll by specifying the full path in Include as above, here's what it should be doing instead:
```
<Reference Include="Microsoft.VisualStudio.Text.Internal">
<HintPath>$(NuGetPackageRoot)\microsoft.visualstudio.text.internal\$(MicrosoftVisualStudioTextInternalVersion)\lib\net46\Microsoft.VisualStudio.Text.Internal.dll</HintPath>
</Reference>
``` | 1.0 | Several build issues around referencing MS.VS.Text.Internal.dll - - [ ] This line should have backslashes and not forward slashes: https://github.com/dotnet/roslyn/blob/08a22f8557a7eecbf1862bdcd92d25a9b1ca3b4e/build/Targets/Versions.props#L61
- [ ] 6 Test projects at EditorFeatures level use this line to reference MS.VS.Text.Internal: https://github.com/dotnet/roslyn/blob/08a22f8557a7eecbf1862bdcd92d25a9b1ca3b4e/src/EditorFeatures/VisualBasicTest/BasicEditorServicesTest.vbproj#L61-L64
- [ ] The Editor's NuGet package for MS.VS.Text.Internal has an empty ref folder - the Editor needs to fix that.
Instead of referencing the .dll by specifying the full path in Include as above, here's what it should be doing instead:
```
<Reference Include="Microsoft.VisualStudio.Text.Internal">
<HintPath>$(NuGetPackageRoot)\microsoft.visualstudio.text.internal\$(MicrosoftVisualStudioTextInternalVersion)\lib\net46\Microsoft.VisualStudio.Text.Internal.dll</HintPath>
</Reference>
``` | non_priority | several build issues around referencing ms vs text internal dll this line should have backslashes and not forward slashes test projects at editorfeatures level use this line to reference ms vs text internal the editor s nuget package for ms vs text internal has an empty ref folder the editor needs to fix that instead of referencing the dll by specifying the full path in include as above here s what it should be doing instead nugetpackageroot microsoft visualstudio text internal microsoftvisualstudiotextinternalversion lib microsoft visualstudio text internal dll | 0 |
95,589 | 16,096,838,620 | IssuesEvent | 2021-04-27 01:56:29 | melsorg/github-scanner-test | https://api.github.com/repos/melsorg/github-scanner-test | opened | CVE-2020-7656 (Medium) detected in jquery-1.6.1.min.js | security vulnerability | ## CVE-2020-7656 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.6.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.6.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.6.1/jquery.min.js</a></p>
<p>Path to dependency file: github-scanner-test/node_modules/follow/browser/index.html</p>
<p>Path to vulnerable library: github-scanner-test/node_modules/follow/browser/jquery-1.6.1.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.6.1.min.js** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jquery prior to 1.9.0 allows Cross-site Scripting attacks via the load method. The load method fails to recognize and remove "<script>" HTML tags that contain a whitespace character, i.e: "</script >", which results in the enclosed script logic to be executed.
<p>Publish Date: 2020-05-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7656>CVE-2020-7656</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-q4m3-2j7h-f7xw">https://github.com/advisories/GHSA-q4m3-2j7h-f7xw</a></p>
<p>Release Date: 2020-05-28</p>
<p>Fix Resolution: jquery - 1.9.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-7656 (Medium) detected in jquery-1.6.1.min.js - ## CVE-2020-7656 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.6.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.6.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.6.1/jquery.min.js</a></p>
<p>Path to dependency file: github-scanner-test/node_modules/follow/browser/index.html</p>
<p>Path to vulnerable library: github-scanner-test/node_modules/follow/browser/jquery-1.6.1.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.6.1.min.js** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jquery prior to 1.9.0 allows Cross-site Scripting attacks via the load method. The load method fails to recognize and remove "<script>" HTML tags that contain a whitespace character, i.e: "</script >", which results in the enclosed script logic to be executed.
<p>Publish Date: 2020-05-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7656>CVE-2020-7656</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-q4m3-2j7h-f7xw">https://github.com/advisories/GHSA-q4m3-2j7h-f7xw</a></p>
<p>Release Date: 2020-05-28</p>
<p>Fix Resolution: jquery - 1.9.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file github scanner test node modules follow browser index html path to vulnerable library github scanner test node modules follow browser jquery min js dependency hierarchy x jquery min js vulnerable library vulnerability details jquery prior to allows cross site scripting attacks via the load method the load method fails to recognize and remove html tags that contain a whitespace character i e which results in the enclosed script logic to be executed publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource | 0 |
36,343 | 7,893,214,204 | IssuesEvent | 2018-06-28 17:18:17 | bridgedotnet/Bridge | https://api.github.com/repos/bridgedotnet/Bridge | closed | Metadata initialization fails when member metadata includes its declaring type | defect in-progress | Relates to Issue #3348:
> When a program uses modules, all entities will be wrapped with `require(["Module"], function(m) { .... } );` to resolve all dependencies first. The problem is that metadata must be initialized after entities are created. The require function changes normal flow of initialization and leads to errors.
The fix for #3348 helps when there are no members referring not initialized types. If such members exist, the issue is reproducible - it causes Bridge to add non-initialized namespace into a metadata class:
```js
// ...
var $m = Bridge.setMetadata,
$n = [System,Demo]; // Error: "Demo" is not defined
$m("Demo.App", function () { ... });
$m("Demo.Test", function () { ... });
```
### Steps To Reproduce
1. Create a solution with 2 Bridge projects named **Demo** and **PrinterModule**.
2. Add the following lines to **PrinterModule/App.cs** to define a module:
```cs
using Bridge;
using System;
namespace PrinterModule
{
[Module(ModuleType.AMD, "PrinterModule")]
public class Printer
{
public void Print(string msg)
{
Console.WriteLine(msg);
}
}
}
```
3. Reference **PrinterModule** project from **Demo** project.
4. Add the following lines to **Demo/App.cs**
```cs
using PrinterModule;
namespace Demo
{
public class App
{
public static void Main()
{
var test = new Test();
test.PrintInfo();
}
}
public class Test
{
// Comment the field below to make the issue disappear.
public static Test Instance = new Test();
public void PrintInfo()
{
var p = new Printer();
var type = GetType();
p.Print(type.FullName + " contains " + type.GetMethods().Length + " method(s).");
}
}
}
```
5. Rebuild the solution
6. Add **require.js** script to the generated HTML file in **Demo** project:
```html
<!DOCTYPE html>
<html lang="en" xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta charset="utf-8" />
<title>Demo</title>
<script src="bridge.js"></script>
<script src="bridge.console.js"></script>
<script src="bridge.meta.js"></script>
<script src="https://cdnjs.cloudflare.com/ajax/libs/require.js/2.3.5/require.js"></script>
<script src="PrinterModule.js"></script>
<script src="Demo.js"></script>
<script src="Demo.meta.js"></script>
</head>
<body>
</body>
</html>
```
7. Open that HTML file in browser.
### Expected Result
No errors. Console output:
```
Demo.Test contains 1 method(s).
```
### Actual Result
Console output:
```
Demo.Test contains 0 method(s).
2 Errors:
Uncaught ReferenceError: Demo is not defined
at Demo.meta.js:6
at Object.Bridge.assembly (bridge.js:3288)
at Demo.meta.js:1
Uncaught TypeError: Cannot read property 'appendChild' of null
at ctor.init (bridge.console.js:314)
at new ctor (bridge.console.js:215)
at Function.get [as instance] (bridge.console.js:22)
at Function.logBase (bridge.console.js:90)
at Function.error (bridge.console.js:122)
at bridge.console.js:83
```
### See also
- https://github.com/Retyped/Retyped/issues/52#issuecomment-384375995 | 1.0 | Metadata initialization fails when member metadata includes its declaring type - Relates to Issue #3348:
> When a program uses modules, all entities will be wrapped with `require(["Module"], function(m) { .... } );` to resolve all dependencies first. The problem is that metadata must be initialized after entities are created. The require function changes normal flow of initialization and leads to errors.
The fix for #3348 helps when there are no members referring not initialized types. If such members exist, the issue is reproducible - it causes Bridge to add non-initialized namespace into a metadata class:
```js
// ...
var $m = Bridge.setMetadata,
$n = [System,Demo]; // Error: "Demo" is not defined
$m("Demo.App", function () { ... });
$m("Demo.Test", function () { ... });
```
### Steps To Reproduce
1. Create a solution with 2 Bridge projects named **Demo** and **PrinterModule**.
2. Add the following lines to **PrinterModule/App.cs** to define a module:
```cs
using Bridge;
using System;
namespace PrinterModule
{
[Module(ModuleType.AMD, "PrinterModule")]
public class Printer
{
public void Print(string msg)
{
Console.WriteLine(msg);
}
}
}
```
3. Reference **PrinterModule** project from **Demo** project.
4. Add the following lines to **Demo/App.cs**
```cs
using PrinterModule;
namespace Demo
{
public class App
{
public static void Main()
{
var test = new Test();
test.PrintInfo();
}
}
public class Test
{
// Comment the field below to make the issue disappear.
public static Test Instance = new Test();
public void PrintInfo()
{
var p = new Printer();
var type = GetType();
p.Print(type.FullName + " contains " + type.GetMethods().Length + " method(s).");
}
}
}
```
5. Rebuild the solution
6. Add **require.js** script to the generated HTML file in **Demo** project:
```html
<!DOCTYPE html>
<html lang="en" xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta charset="utf-8" />
<title>Demo</title>
<script src="bridge.js"></script>
<script src="bridge.console.js"></script>
<script src="bridge.meta.js"></script>
<script src="https://cdnjs.cloudflare.com/ajax/libs/require.js/2.3.5/require.js"></script>
<script src="PrinterModule.js"></script>
<script src="Demo.js"></script>
<script src="Demo.meta.js"></script>
</head>
<body>
</body>
</html>
```
7. Open that HTML file in browser.
### Expected Result
No errors. Console output:
```
Demo.Test contains 1 method(s).
```
### Actual Result
Console output:
```
Demo.Test contains 0 method(s).
2 Errors:
Uncaught ReferenceError: Demo is not defined
at Demo.meta.js:6
at Object.Bridge.assembly (bridge.js:3288)
at Demo.meta.js:1
Uncaught TypeError: Cannot read property 'appendChild' of null
at ctor.init (bridge.console.js:314)
at new ctor (bridge.console.js:215)
at Function.get [as instance] (bridge.console.js:22)
at Function.logBase (bridge.console.js:90)
at Function.error (bridge.console.js:122)
at bridge.console.js:83
```
### See also
- https://github.com/Retyped/Retyped/issues/52#issuecomment-384375995 | non_priority | metadata initialization fails when member metadata includes its declaring type relates to issue when a program uses modules all entities will be wrapped with require function m to resolve all dependencies first the problem is that metadata must be initialized after entities are created the require function changes normal flow of initialization and leads to errors the fix for helps when there are no members referring not initialized types if such members exist the issue is reproducible it causes bridge to add non initialized namespace into a metadata class js var m bridge setmetadata n error demo is not defined m demo app function m demo test function steps to reproduce create a solution with bridge projects named demo and printermodule add the following lines to printermodule app cs to define a module cs using bridge using system namespace printermodule public class printer public void print string msg console writeline msg reference printermodule project from demo project add the following lines to demo app cs cs using printermodule namespace demo public class app public static void main var test new test test printinfo public class test comment the field below to make the issue disappear public static test instance new test public void printinfo var p new printer var type gettype p print type fullname contains type getmethods length method s rebuild the solution add require js script to the generated html file in demo project html html lang en xmlns demo script src open that html file in browser expected result no errors console output demo test contains method s actual result console output demo test contains method s errors uncaught referenceerror demo is not defined at demo meta js at object bridge assembly bridge js at demo meta js uncaught typeerror cannot read property appendchild of null at ctor init bridge console js at new ctor bridge console js at function get bridge console js at function logbase bridge console js at function error bridge console js at bridge console js see also | 0 |
1,207 | 2,754,976,195 | IssuesEvent | 2015-04-26 06:38:32 | stamp-web/stamp-web-aurelia | https://api.github.com/repos/stamp-web/stamp-web-aurelia | closed | Provide the ability to change the sort attribute on the stamp-list | enhancement usability | Provide a drop down to allow selection of the sorting attribute for the stamp list. | True | Provide the ability to change the sort attribute on the stamp-list - Provide a drop down to allow selection of the sorting attribute for the stamp list. | non_priority | provide the ability to change the sort attribute on the stamp list provide a drop down to allow selection of the sorting attribute for the stamp list | 0 |
303,578 | 26,217,419,028 | IssuesEvent | 2023-01-04 12:11:53 | EddieHubCommunity/LinkFree | https://api.github.com/repos/EddieHubCommunity/LinkFree | closed | New Testimonial test | testimonial | ### Name
eddiejaoude2
### Title
test
### Description
EddieHub is the first community to help me start my journey to Open Source. I wasn't aware of anything called **"Open Source"** before I met @eddiejaoude on a Twitter space and came across **EddieHub community** and found so many people here geeking out, helping each other, making PRs and issues, and many more. The repositories maintainers are so kind here; always ready to help each other.
I created my first issue and PR here and contributed to this community and soon became a member. It helped me to customize my GitHub profile and taught me how to collaborate with people all over the world.
I'm very happy being here as a member now and helping people geeking out together and learning new things. ❤️
Thank you Eddie Sir for making this awesome community! 🚀
EddieHub is invaluable: It's beyond any ratings :) | 1.0 | New Testimonial test - ### Name
eddiejaoude2
### Title
test
### Description
EddieHub is the first community to help me start my journey to Open Source. I wasn't aware of anything called **"Open Source"** before I met @eddiejaoude on a Twitter space and came across **EddieHub community** and found so many people here geeking out, helping each other, making PRs and issues, and many more. The repositories maintainers are so kind here; always ready to help each other.
I created my first issue and PR here and contributed to this community and soon became a member. It helped me to customize my GitHub profile and taught me how to collaborate with people all over the world.
I'm very happy being here as a member now and helping people geeking out together and learning new things. ❤️
Thank you Eddie Sir for making this awesome community! 🚀
EddieHub is invaluable: It's beyond any ratings :) | non_priority | new testimonial test name title test description eddiehub is the first community to help me start my journey to open source i wasn t aware of anything called open source before i met eddiejaoude on a twitter space and came across eddiehub community and found so many people here geeking out helping each other making prs and issues and many more the repositories maintainers are so kind here always ready to help each other i created my first issue and pr here and contributed to this community and soon became a member it helped me to customize my github profile and taught me how to collaborate with people all over the world i m very happy being here as a member now and helping people geeking out together and learning new things ❤️ thank you eddie sir for making this awesome community 🚀 eddiehub is invaluable it s beyond any ratings | 0 |
372,220 | 25,988,070,773 | IssuesEvent | 2022-12-20 03:29:55 | yugabyte/yugabyte-db | https://api.github.com/repos/yugabyte/yugabyte-db | opened | [Docs] IP allow lists | area/documentation | ### Description
# Issues
Could not find the feature as documentation in IP allow list
# Description
HI team,
It seems the feature of `Enable public access` is documented but is not implemented in cloud.yugabyte.com.
https://github.com/yugabyte/yugabyte-db/commit/2bd3100f9a1c85bb7b7f3112ec4323abf876677e
I wonder it will be released soon, but could you please check for it?
https://docs.yugabyte.com/preview/yugabyte-cloud/cloud-secure-clusters/add-connections/#enabling-public-access
# Expectation | 1.0 | [Docs] IP allow lists - ### Description
# Issues
Could not find the feature as documentation in IP allow list
# Description
HI team,
It seems the feature of `Enable public access` is documented but is not implemented in cloud.yugabyte.com.
https://github.com/yugabyte/yugabyte-db/commit/2bd3100f9a1c85bb7b7f3112ec4323abf876677e
I wonder it will be released soon, but could you please check for it?
https://docs.yugabyte.com/preview/yugabyte-cloud/cloud-secure-clusters/add-connections/#enabling-public-access
# Expectation | non_priority | ip allow lists description issues could not find the feature as documentation in ip allow list description hi team it seems the feature of enable public access is documented but is not implemented in cloud yugabyte com i wonder it will be released soon but could you please check for it expectation | 0 |
196,508 | 22,442,051,348 | IssuesEvent | 2022-06-21 02:28:32 | haeli05/source | https://api.github.com/repos/haeli05/source | opened | CVE-2022-33987 (Medium) detected in got-6.7.1.tgz | security vulnerability | ## CVE-2022-33987 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>got-6.7.1.tgz</b></p></summary>
<p>Simplified HTTP requests</p>
<p>Library home page: <a href="https://registry.npmjs.org/got/-/got-6.7.1.tgz">https://registry.npmjs.org/got/-/got-6.7.1.tgz</a></p>
<p>Path to dependency file: /FrontEnd/package.json</p>
<p>Path to vulnerable library: /FrontEnd/node_modules/npm/node_modules/got/package.json,/FrontEnd/node_modules/npm/node_modules/got/package.json</p>
<p>
Dependency Hierarchy:
- nodemon-1.18.10.tgz (Root Library)
- update-notifier-2.5.0.tgz
- latest-version-3.1.0.tgz
- package-json-4.0.1.tgz
- :x: **got-6.7.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The got package before 12.1.0 for Node.js allows a redirect to a UNIX socket.
<p>Publish Date: 2022-06-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-33987>CVE-2022-33987</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-33987">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-33987</a></p>
<p>Release Date: 2022-06-18</p>
<p>Fix Resolution: got - 11.8.5,12.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-33987 (Medium) detected in got-6.7.1.tgz - ## CVE-2022-33987 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>got-6.7.1.tgz</b></p></summary>
<p>Simplified HTTP requests</p>
<p>Library home page: <a href="https://registry.npmjs.org/got/-/got-6.7.1.tgz">https://registry.npmjs.org/got/-/got-6.7.1.tgz</a></p>
<p>Path to dependency file: /FrontEnd/package.json</p>
<p>Path to vulnerable library: /FrontEnd/node_modules/npm/node_modules/got/package.json,/FrontEnd/node_modules/npm/node_modules/got/package.json</p>
<p>
Dependency Hierarchy:
- nodemon-1.18.10.tgz (Root Library)
- update-notifier-2.5.0.tgz
- latest-version-3.1.0.tgz
- package-json-4.0.1.tgz
- :x: **got-6.7.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The got package before 12.1.0 for Node.js allows a redirect to a UNIX socket.
<p>Publish Date: 2022-06-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-33987>CVE-2022-33987</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-33987">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-33987</a></p>
<p>Release Date: 2022-06-18</p>
<p>Fix Resolution: got - 11.8.5,12.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in got tgz cve medium severity vulnerability vulnerable library got tgz simplified http requests library home page a href path to dependency file frontend package json path to vulnerable library frontend node modules npm node modules got package json frontend node modules npm node modules got package json dependency hierarchy nodemon tgz root library update notifier tgz latest version tgz package json tgz x got tgz vulnerable library vulnerability details the got package before for node js allows a redirect to a unix socket publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution got step up your open source security game with mend | 0 |
16,696 | 5,272,512,681 | IssuesEvent | 2017-02-06 13:09:12 | purescript/purescript | https://api.github.com/repos/purescript/purescript | closed | Avoid IIFE definitions in generated JavaScript | codegen | Tagging this with discussion, because I'm not sure if doing so is problematic.
An example of the offending code:
``` javascript
var Just = (function () {
function Just(value0) {
this.value0 = value0;
};
Just.create = function (value0) {
return new Just(value0);
};
return Just;
})();
var Nothing = (function () {
function Nothing() {
};
Nothing.value = new Nothing();
return Nothing;
})();
```
The IIFE exists so that the definition of `Just` and `Nothing` do not involve statements at the module level (the `create` / `value` property assignments). In theory this makes them _easier_ to erase, since the whole value can be eliminated, but apparently Uglify considers this to be side-effectful. I assume it takes that stance with any IIFE definition, since here only values in the internal scope of the IIFE are referenced.
I actually don't remember exactly why I did introduce the IIFE... it may purely be to avoid the module-level statements, or perhaps codegen can only produce single AST values for declarations. The latter wouldn't be too much of a problem to change, it's just a bit of refactoring.
/cc @AppShipIt @spicydonuts
| 1.0 | Avoid IIFE definitions in generated JavaScript - Tagging this with discussion, because I'm not sure if doing so is problematic.
An example of the offending code:
``` javascript
var Just = (function () {
function Just(value0) {
this.value0 = value0;
};
Just.create = function (value0) {
return new Just(value0);
};
return Just;
})();
var Nothing = (function () {
function Nothing() {
};
Nothing.value = new Nothing();
return Nothing;
})();
```
The IIFE exists so that the definition of `Just` and `Nothing` do not involve statements at the module level (the `create` / `value` property assignments). In theory this makes them _easier_ to erase, since the whole value can be eliminated, but apparently Uglify considers this to be side-effectful. I assume it takes that stance with any IIFE definition, since here only values in the internal scope of the IIFE are referenced.
I actually don't remember exactly why I did introduce the IIFE... it may purely be to avoid the module-level statements, or perhaps codegen can only produce single AST values for declarations. The latter wouldn't be too much of a problem to change, it's just a bit of refactoring.
/cc @AppShipIt @spicydonuts
| non_priority | avoid iife definitions in generated javascript tagging this with discussion because i m not sure if doing so is problematic an example of the offending code javascript var just function function just this just create function return new just return just var nothing function function nothing nothing value new nothing return nothing the iife exists so that the definition of just and nothing do not involve statements at the module level the create value property assignments in theory this makes them easier to erase since the whole value can be eliminated but apparently uglify considers this to be side effectful i assume it takes that stance with any iife definition since here only values in the internal scope of the iife are referenced i actually don t remember exactly why i did introduce the iife it may purely be to avoid the module level statements or perhaps codegen can only produce single ast values for declarations the latter wouldn t be too much of a problem to change it s just a bit of refactoring cc appshipit spicydonuts | 0 |
243,405 | 20,384,422,045 | IssuesEvent | 2022-02-22 04:19:38 | DnD-Montreal/session-tome | https://api.github.com/repos/DnD-Montreal/session-tome | opened | Cypress Tests for Campaign Entry Creation | task test | ## Description
<!-- Provide a general summary of the feature in the title above -->
Write E2E Cypress tests for #252 Campaign Entry Creation.
## Possible Implementation
<!-- If you have an idea of how to implement the issue, jot it down here - this section is optional -->
- Check creation of campaigns for other members | 1.0 | Cypress Tests for Campaign Entry Creation - ## Description
<!-- Provide a general summary of the feature in the title above -->
Write E2E Cypress tests for #252 Campaign Entry Creation.
## Possible Implementation
<!-- If you have an idea of how to implement the issue, jot it down here - this section is optional -->
- Check creation of campaigns for other members | non_priority | cypress tests for campaign entry creation description write cypress tests for campaign entry creation possible implementation check creation of campaigns for other members | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.