Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
234,677 | 19,215,314,326 | IssuesEvent | 2021-12-07 08:52:10 | lutraconsulting/input-manual-tests | https://api.github.com/repos/lutraconsulting/input-manual-tests | opened | Test Execution InputApp 1.2.0 (android) | test execution | ## Test plan for Input manual testing
| Test environment | Value |
|---|---|
| Input Version: | 1.2.0. 8bb249d |
| Mergin Version: | 2021.11 |
| Mergin URL: <> | https://public.cloudmergin.com |
| QGIS Version: | 3.16 |
| Mergin plugin Version: | 2021.4.3 |
| Mobile OS: iOS/Android */Windows | Android arm64-v8a |
| Date of Execution: | 7.12.2021 |
* For Android please also state type of used architecture ( armeabi-v7a / arm64-v8a )
---
### Test Cases
- [ ] ( #2 ) TC 01: Mergin & Projects Manipulation
- [ ] ( #3 ) TC 02: Sync & Project Status
- [ ] ( #51 ) TC 03: Map Canvas
- [ ] ( #5 ) TC 04: Recording
- [ ] ( #6 ) TC 05: Forms
- [ ] ( #7 ) TC 06: Data Providers
- [ ] ( #8 ) TC 07: Translations
- [ ] ( #18 ) TC 08: System Specifics
- [ ] ( #19 ) TC 09: Welcome Screen & Project
- [ ] ( #46 ) TC 10: Proj Tests
- [ ] ( #50 ) TC 11: Subscriptions
- [ ] ( #48 ) TC 12: Tickets
- [ ] ( #49 ) TC 13: GPS
---
| Test Execution Outcome | |
|---|---|
| Issues Created During Testing: | LINK TO ISSUE(S) |
**Success** / **Bugs Created** (erase one) | 1.0 | Test Execution InputApp 1.2.0 (android) - ## Test plan for Input manual testing
| Test environment | Value |
|---|---|
| Input Version: | 1.2.0. 8bb249d |
| Mergin Version: | 2021.11 |
| Mergin URL: <> | https://public.cloudmergin.com |
| QGIS Version: | 3.16 |
| Mergin plugin Version: | 2021.4.3 |
| Mobile OS: iOS/Android */Windows | Android arm64-v8a |
| Date of Execution: | 7.12.2021 |
* For Android please also state type of used architecture ( armeabi-v7a / arm64-v8a )
---
### Test Cases
- [ ] ( #2 ) TC 01: Mergin & Projects Manipulation
- [ ] ( #3 ) TC 02: Sync & Project Status
- [ ] ( #51 ) TC 03: Map Canvas
- [ ] ( #5 ) TC 04: Recording
- [ ] ( #6 ) TC 05: Forms
- [ ] ( #7 ) TC 06: Data Providers
- [ ] ( #8 ) TC 07: Translations
- [ ] ( #18 ) TC 08: System Specifics
- [ ] ( #19 ) TC 09: Welcome Screen & Project
- [ ] ( #46 ) TC 10: Proj Tests
- [ ] ( #50 ) TC 11: Subscriptions
- [ ] ( #48 ) TC 12: Tickets
- [ ] ( #49 ) TC 13: GPS
---
| Test Execution Outcome | |
|---|---|
| Issues Created During Testing: | LINK TO ISSUE(S) |
**Success** / **Bugs Created** (erase one) | non_priority | test execution inputapp android test plan for input manual testing test environment value input version mergin version mergin url qgis version mergin plugin version mobile os ios android windows android date of execution for android please also state type of used architecture armeabi test cases tc mergin projects manipulation tc sync project status tc map canvas tc recording tc forms tc data providers tc translations tc system specifics tc welcome screen project tc proj tests tc subscriptions tc tickets tc gps test execution outcome issues created during testing link to issue s success bugs created erase one | 0 |
113,813 | 11,824,835,112 | IssuesEvent | 2020-03-21 09:09:48 | dankamongmen/notcurses | https://api.github.com/repos/dankamongmen/notcurses | closed | Add `ncplane_mergedown` | documentation enhancement | Like Photoshop and the GIMP, it would be useful to have `ncplane_mergedown`. This would take as its arguments at least:
`ncplane_merge(ncplane* restrict n1, ncplane* restrict n2)`
both n1 and n2 must be non-NULL, and must be distinct (hence the `restrict`). whichever one is above is the source; the one below is the target. only the target will exist at the end of the call.
1) if necessary, the target is resized to the minimum perimeter enclosing both ncplanes in their current positions. if there is no intersection between n1 and n2, the new area will be at least the sum of both areas, and can be larger.
2) the new plane is initialized via the rendering process, as applied to the two planes in isolation. thus, opaque cells on the top plane define target cells entirely; transparent cells on the top plane define target cells not at all; double transparency results in transparency, etc. | 1.0 | Add `ncplane_mergedown` - Like Photoshop and the GIMP, it would be useful to have `ncplane_mergedown`. This would take as its arguments at least:
`ncplane_merge(ncplane* restrict n1, ncplane* restrict n2)`
both n1 and n2 must be non-NULL, and must be distinct (hence the `restrict`). whichever one is above is the source; the one below is the target. only the target will exist at the end of the call.
1) if necessary, the target is resized to the minimum perimeter enclosing both ncplanes in their current positions. if there is no intersection between n1 and n2, the new area will be at least the sum of both areas, and can be larger.
2) the new plane is initialized via the rendering process, as applied to the two planes in isolation. thus, opaque cells on the top plane define target cells entirely; transparent cells on the top plane define target cells not at all; double transparency results in transparency, etc. | non_priority | add ncplane mergedown like photoshop and the gimp it would be useful to have ncplane mergedown this would take as its arguments at least ncplane merge ncplane restrict ncplane restrict both and must be non null and must be distinct hence the restrict whichever one is above is the source the one below is the target only the target will exist at the end of the call if necessary the target is resized to the minimum perimeter enclosing both ncplanes in their current positions if there is no intersection between and the new area will be at least the sum of both areas and can be larger the new plane is initialized via the rendering process as applied to the two planes in isolation thus opaque cells on the top plane define target cells entirely transparent cells on the top plane define target cells not at all double transparency results in transparency etc | 0 |
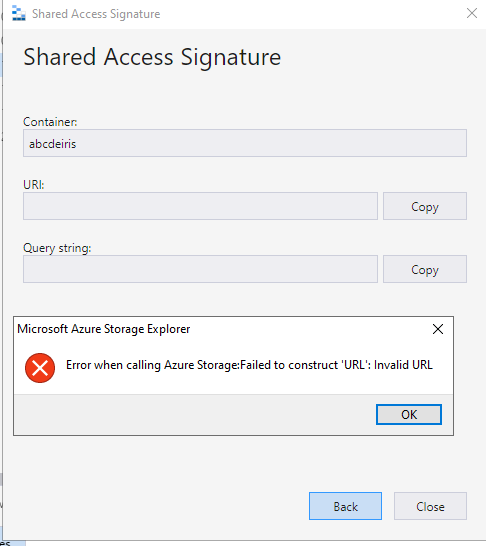
147,533 | 11,795,440,368 | IssuesEvent | 2020-03-18 08:58:08 | microsoft/AzureStorageExplorer | https://api.github.com/repos/microsoft/AzureStorageExplorer | opened | An error occurs when creating sas for one blob container under name & key attached account | :beetle: regression :gear: attach :gear: blobs 🧪 testing | **Storage Explorer Version:** 1.12.0
**Build**: [20200318.5](https://devdiv.visualstudio.com/DevDiv/_build/results?buildId=3561251
)
**Branch**: master
**Platform/OS:** Windows 10/ Linux Ubuntu 19.04/ macOS High Sierra
**Architecture**: ia32/x64
**Regression From:** Previous release(1.12.0)
**Steps to reproduce:**
1. Attach one Non-ADLS Gen2 storage account via name & key.
2. Expand the attached storage account -> Blob Containers.
3. Create a new blob container -> Right click it -> Click 'Get Shared Access Signature...'
4. Click 'Create' in the sas dialog and check the result.
**Expect Experience:**
1. No error occurs.
2. URI and Query string show well.
**Actual Experience:**
An error pops up.
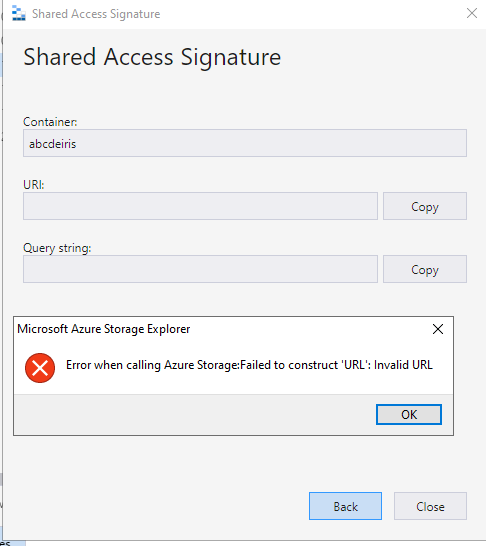
**More Info:**
This issue also reproduce for one blob under name & key attached account. | 1.0 | An error occurs when creating sas for one blob container under name & key attached account - **Storage Explorer Version:** 1.12.0
**Build**: [20200318.5](https://devdiv.visualstudio.com/DevDiv/_build/results?buildId=3561251
)
**Branch**: master
**Platform/OS:** Windows 10/ Linux Ubuntu 19.04/ macOS High Sierra
**Architecture**: ia32/x64
**Regression From:** Previous release(1.12.0)
**Steps to reproduce:**
1. Attach one Non-ADLS Gen2 storage account via name & key.
2. Expand the attached storage account -> Blob Containers.
3. Create a new blob container -> Right click it -> Click 'Get Shared Access Signature...'
4. Click 'Create' in the sas dialog and check the result.
**Expect Experience:**
1. No error occurs.
2. URI and Query string show well.
**Actual Experience:**
An error pops up.
**More Info:**
This issue also reproduce for one blob under name & key attached account. | non_priority | an error occurs when creating sas for one blob container under name key attached account storage explorer version build branch master platform os windows linux ubuntu macos high sierra architecture regression from previous release steps to reproduce attach one non adls storage account via name key expand the attached storage account blob containers create a new blob container right click it click get shared access signature click create in the sas dialog and check the result expect experience no error occurs uri and query string show well actual experience an error pops up more info this issue also reproduce for one blob under name key attached account | 0 |
14,957 | 9,437,098,728 | IssuesEvent | 2019-04-13 12:39:37 | josh-tf/cbvpos | https://api.github.com/repos/josh-tf/cbvpos | closed | CVE-2016-10540 High Severity Vulnerability detected by WhiteSource | security vulnerability | ## CVE-2016-10540 - High Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimatch-0.3.0.tgz</b>, <b>minimatch-0.2.14.tgz</b>, <b>minimatch-2.0.10.tgz</b></p></summary>
<p>
<details><summary><b>minimatch-0.3.0.tgz</b></p></summary>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="http://registry.npmjs.org/minimatch/-/minimatch-0.3.0.tgz">http://registry.npmjs.org/minimatch/-/minimatch-0.3.0.tgz</a></p>
<p>Path to dependency file: /cbvpos/app/package.json</p>
<p>Path to vulnerable library: /tmp/git/cbvpos/app/node_modules/mocha/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- mocha-2.5.3.tgz (Root Library)
- glob-3.2.11.tgz
- :x: **minimatch-0.3.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimatch-0.2.14.tgz</b></p></summary>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="http://registry.npmjs.org/minimatch/-/minimatch-0.2.14.tgz">http://registry.npmjs.org/minimatch/-/minimatch-0.2.14.tgz</a></p>
<p>Path to dependency file: /cbvpos/app/package.json</p>
<p>Path to vulnerable library: /tmp/git/cbvpos/app/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- grunt-0.4.5.tgz (Root Library)
- :x: **minimatch-0.2.14.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimatch-2.0.10.tgz</b></p></summary>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="http://registry.npmjs.org/minimatch/-/minimatch-2.0.10.tgz">http://registry.npmjs.org/minimatch/-/minimatch-2.0.10.tgz</a></p>
<p>Path to dependency file: /cbvpos/app/package.json</p>
<p>Path to vulnerable library: /tmp/git/cbvpos/app/node_modules/bower/lib/node_modules/glob/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- grunt-bowercopy-1.2.4.tgz (Root Library)
- glob-4.5.3.tgz
- :x: **minimatch-2.0.10.tgz** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Minimatch is a minimal matching utility that works by converting glob expressions into JavaScript `RegExp` objects. The primary function, `minimatch(path, pattern)` in Minimatch 3.0.1 and earlier is vulnerable to ReDoS in the `pattern` parameter.
<p>Publish Date: 2018-05-31
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10540>CVE-2016-10540</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/118">https://nodesecurity.io/advisories/118</a></p>
<p>Release Date: 2016-06-20</p>
<p>Fix Resolution: Update to version 3.0.2 or later.</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isOpenPROnNewVersion":false,"isPackageBased":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimatch","packageVersion":"0.3.0","isTransitiveDependency":true,"dependencyTree":"mocha:2.5.3;glob:3.2.11;minimatch:0.3.0","isMinimumFixVersionAvailable":false},{"packageType":"javascript/Node.js","packageName":"minimatch","packageVersion":"0.2.14","isTransitiveDependency":true,"dependencyTree":"grunt:0.4.5;minimatch:0.2.14","isMinimumFixVersionAvailable":false},{"packageType":"javascript/Node.js","packageName":"minimatch","packageVersion":"2.0.10","isTransitiveDependency":true,"dependencyTree":"grunt-bowercopy:1.2.4;glob:4.5.3;minimatch:2.0.10","isMinimumFixVersionAvailable":false}],"vulnerabilityIdentifier":"CVE-2016-10540","vulnerabilityDetails":"Minimatch is a minimal matching utility that works by converting glob expressions into JavaScript `RegExp` objects. The primary function, `minimatch(path, pattern)` in Minimatch 3.0.1 and earlier is vulnerable to ReDoS in the `pattern` parameter.","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2016-10540 High Severity Vulnerability detected by WhiteSource - ## CVE-2016-10540 - High Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimatch-0.3.0.tgz</b>, <b>minimatch-0.2.14.tgz</b>, <b>minimatch-2.0.10.tgz</b></p></summary>
<p>
<details><summary><b>minimatch-0.3.0.tgz</b></p></summary>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="http://registry.npmjs.org/minimatch/-/minimatch-0.3.0.tgz">http://registry.npmjs.org/minimatch/-/minimatch-0.3.0.tgz</a></p>
<p>Path to dependency file: /cbvpos/app/package.json</p>
<p>Path to vulnerable library: /tmp/git/cbvpos/app/node_modules/mocha/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- mocha-2.5.3.tgz (Root Library)
- glob-3.2.11.tgz
- :x: **minimatch-0.3.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimatch-0.2.14.tgz</b></p></summary>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="http://registry.npmjs.org/minimatch/-/minimatch-0.2.14.tgz">http://registry.npmjs.org/minimatch/-/minimatch-0.2.14.tgz</a></p>
<p>Path to dependency file: /cbvpos/app/package.json</p>
<p>Path to vulnerable library: /tmp/git/cbvpos/app/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- grunt-0.4.5.tgz (Root Library)
- :x: **minimatch-0.2.14.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimatch-2.0.10.tgz</b></p></summary>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="http://registry.npmjs.org/minimatch/-/minimatch-2.0.10.tgz">http://registry.npmjs.org/minimatch/-/minimatch-2.0.10.tgz</a></p>
<p>Path to dependency file: /cbvpos/app/package.json</p>
<p>Path to vulnerable library: /tmp/git/cbvpos/app/node_modules/bower/lib/node_modules/glob/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- grunt-bowercopy-1.2.4.tgz (Root Library)
- glob-4.5.3.tgz
- :x: **minimatch-2.0.10.tgz** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Minimatch is a minimal matching utility that works by converting glob expressions into JavaScript `RegExp` objects. The primary function, `minimatch(path, pattern)` in Minimatch 3.0.1 and earlier is vulnerable to ReDoS in the `pattern` parameter.
<p>Publish Date: 2018-05-31
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10540>CVE-2016-10540</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/118">https://nodesecurity.io/advisories/118</a></p>
<p>Release Date: 2016-06-20</p>
<p>Fix Resolution: Update to version 3.0.2 or later.</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isOpenPROnNewVersion":false,"isPackageBased":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimatch","packageVersion":"0.3.0","isTransitiveDependency":true,"dependencyTree":"mocha:2.5.3;glob:3.2.11;minimatch:0.3.0","isMinimumFixVersionAvailable":false},{"packageType":"javascript/Node.js","packageName":"minimatch","packageVersion":"0.2.14","isTransitiveDependency":true,"dependencyTree":"grunt:0.4.5;minimatch:0.2.14","isMinimumFixVersionAvailable":false},{"packageType":"javascript/Node.js","packageName":"minimatch","packageVersion":"2.0.10","isTransitiveDependency":true,"dependencyTree":"grunt-bowercopy:1.2.4;glob:4.5.3;minimatch:2.0.10","isMinimumFixVersionAvailable":false}],"vulnerabilityIdentifier":"CVE-2016-10540","vulnerabilityDetails":"Minimatch is a minimal matching utility that works by converting glob expressions into JavaScript `RegExp` objects. The primary function, `minimatch(path, pattern)` in Minimatch 3.0.1 and earlier is vulnerable to ReDoS in the `pattern` parameter.","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high severity vulnerability detected by whitesource cve high severity vulnerability vulnerable libraries minimatch tgz minimatch tgz minimatch tgz minimatch tgz a glob matcher in javascript library home page a href path to dependency file cbvpos app package json path to vulnerable library tmp git cbvpos app node modules mocha node modules minimatch package json dependency hierarchy mocha tgz root library glob tgz x minimatch tgz vulnerable library minimatch tgz a glob matcher in javascript library home page a href path to dependency file cbvpos app package json path to vulnerable library tmp git cbvpos app node modules minimatch package json dependency hierarchy grunt tgz root library x minimatch tgz vulnerable library minimatch tgz a glob matcher in javascript library home page a href path to dependency file cbvpos app package json path to vulnerable library tmp git cbvpos app node modules bower lib node modules glob node modules minimatch package json dependency hierarchy grunt bowercopy tgz root library glob tgz x minimatch tgz vulnerable library vulnerability details minimatch is a minimal matching utility that works by converting glob expressions into javascript regexp objects the primary function minimatch path pattern in minimatch and earlier is vulnerable to redos in the pattern parameter publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution update to version or later step up your open source security game with whitesource isopenpronvulnerability true isopenpronnewversion false ispackagebased true packages vulnerabilityidentifier cve vulnerabilitydetails minimatch is a minimal matching utility that works by converting glob expressions into javascript regexp objects the primary function minimatch path pattern in minimatch and earlier is vulnerable to redos in the pattern parameter high a high ac low pr none s unchanged c none ui none av network i none extradata | 0 |
105,564 | 11,454,642,349 | IssuesEvent | 2020-02-06 17:27:36 | CarlaValverde/Tarjeta- | https://api.github.com/repos/CarlaValverde/Tarjeta- | closed | Actualización de una Interfaz | documentation enhancement implementation improvement | En la siguiente tarea se deberá llevar a cabo la actualización de la interfaz TarjetaDébito creada anteriormente, para ello se le añadirán dos nuevos métodos:
- métodos de obtención y establecimiento de los atributos necesarios en las funciones compra y retirarCajero. | 1.0 | Actualización de una Interfaz - En la siguiente tarea se deberá llevar a cabo la actualización de la interfaz TarjetaDébito creada anteriormente, para ello se le añadirán dos nuevos métodos:
- métodos de obtención y establecimiento de los atributos necesarios en las funciones compra y retirarCajero. | non_priority | actualización de una interfaz en la siguiente tarea se deberá llevar a cabo la actualización de la interfaz tarjetadébito creada anteriormente para ello se le añadirán dos nuevos métodos métodos de obtención y establecimiento de los atributos necesarios en las funciones compra y retirarcajero | 0 |
221,906 | 17,029,812,768 | IssuesEvent | 2021-07-04 10:31:23 | bytevictor/memeHub | https://api.github.com/repos/bytevictor/memeHub | opened | [DOC] Implementación: explica bien las fases | documentation | No cuentes lo que has hecho, cuenta los problemas que has resuelto.Como te planteaste las diferentes fases de la misma, qué productos mínimamente viables creaste, qué cosas fuiste añadiendo poco a poco, los problemas de rendering del canvas, en general todos los problemas que me has ido comentando, usando como hilo conductor la secuencia de MVPs.
También como en cada una de las fases te has ajustado a las HUs que tenías desde el principio. | 1.0 | [DOC] Implementación: explica bien las fases - No cuentes lo que has hecho, cuenta los problemas que has resuelto.Como te planteaste las diferentes fases de la misma, qué productos mínimamente viables creaste, qué cosas fuiste añadiendo poco a poco, los problemas de rendering del canvas, en general todos los problemas que me has ido comentando, usando como hilo conductor la secuencia de MVPs.
También como en cada una de las fases te has ajustado a las HUs que tenías desde el principio. | non_priority | implementación explica bien las fases no cuentes lo que has hecho cuenta los problemas que has resuelto como te planteaste las diferentes fases de la misma qué productos mínimamente viables creaste qué cosas fuiste añadiendo poco a poco los problemas de rendering del canvas en general todos los problemas que me has ido comentando usando como hilo conductor la secuencia de mvps también como en cada una de las fases te has ajustado a las hus que tenías desde el principio | 0 |
128,398 | 18,048,205,527 | IssuesEvent | 2021-09-19 09:09:04 | jinhogate/pizza_angular | https://api.github.com/repos/jinhogate/pizza_angular | opened | CVE-2018-19837 (Medium) detected in node-sass-4.9.3.tgz | security vulnerability | ## CVE-2018-19837 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sass-4.9.3.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.9.3.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.9.3.tgz</a></p>
<p>
Dependency Hierarchy:
- build-angular-0.6.8.tgz (Root Library)
- :x: **node-sass-4.9.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jinhogate/pizza_angular/commit/353ead6609cbe90c767728d4050746689c22c532">353ead6609cbe90c767728d4050746689c22c532</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass prior to 3.5.5, Sass::Eval::operator()(Sass::Binary_Expression*) inside eval.cpp allows attackers to cause a denial-of-service resulting from stack consumption via a crafted sass file, because of certain incorrect parsing of '%' as a modulo operator in parser.cpp.
<p>Publish Date: 2018-12-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19837>CVE-2018-19837</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sass/libsass/releases/tag/3.5.5">https://github.com/sass/libsass/releases/tag/3.5.5</a></p>
<p>Release Date: 2018-12-04</p>
<p>Fix Resolution: libsass - 3.5.5;node-sass - 4.14.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-19837 (Medium) detected in node-sass-4.9.3.tgz - ## CVE-2018-19837 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sass-4.9.3.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.9.3.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.9.3.tgz</a></p>
<p>
Dependency Hierarchy:
- build-angular-0.6.8.tgz (Root Library)
- :x: **node-sass-4.9.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jinhogate/pizza_angular/commit/353ead6609cbe90c767728d4050746689c22c532">353ead6609cbe90c767728d4050746689c22c532</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass prior to 3.5.5, Sass::Eval::operator()(Sass::Binary_Expression*) inside eval.cpp allows attackers to cause a denial-of-service resulting from stack consumption via a crafted sass file, because of certain incorrect parsing of '%' as a modulo operator in parser.cpp.
<p>Publish Date: 2018-12-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19837>CVE-2018-19837</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sass/libsass/releases/tag/3.5.5">https://github.com/sass/libsass/releases/tag/3.5.5</a></p>
<p>Release Date: 2018-12-04</p>
<p>Fix Resolution: libsass - 3.5.5;node-sass - 4.14.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in node sass tgz cve medium severity vulnerability vulnerable library node sass tgz wrapper around libsass library home page a href dependency hierarchy build angular tgz root library x node sass tgz vulnerable library found in head commit a href found in base branch master vulnerability details in libsass prior to sass eval operator sass binary expression inside eval cpp allows attackers to cause a denial of service resulting from stack consumption via a crafted sass file because of certain incorrect parsing of as a modulo operator in parser cpp publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution libsass node sass step up your open source security game with whitesource | 0 |
50,952 | 6,136,497,864 | IssuesEvent | 2017-06-26 09:32:25 | RachelDavids/RuleChecker | https://api.github.com/repos/RachelDavids/RuleChecker | opened | false positive ? Speculative Generality | bug test case | class has one ctor and one method ...
DifferenceStateList.cs (1 item)
Error Gendarme.Rules.Smells.AvoidSpeculativeGeneralityRule(2.10): Gendarme.Rules.Smells.AvoidSpeculativeGeneralityRule(2.10): If you will need the feature in the future then you should implement it in the future.
This class contains a lot of methods that only delegates the call to other. This kind of Delegation could be a sign for Speculative Generality (5)
| 1.0 | false positive ? Speculative Generality - class has one ctor and one method ...
DifferenceStateList.cs (1 item)
Error Gendarme.Rules.Smells.AvoidSpeculativeGeneralityRule(2.10): Gendarme.Rules.Smells.AvoidSpeculativeGeneralityRule(2.10): If you will need the feature in the future then you should implement it in the future.
This class contains a lot of methods that only delegates the call to other. This kind of Delegation could be a sign for Speculative Generality (5)
| non_priority | false positive speculative generality class has one ctor and one method differencestatelist cs item error gendarme rules smells avoidspeculativegeneralityrule gendarme rules smells avoidspeculativegeneralityrule if you will need the feature in the future then you should implement it in the future this class contains a lot of methods that only delegates the call to other this kind of delegation could be a sign for speculative generality | 0 |
304,743 | 26,329,429,272 | IssuesEvent | 2023-01-10 09:40:21 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | opened | Test failure: PlaylistServiceUnitTest.CreateAndRemovePlaylist | QA/No release-notes/exclude ci-concern bot/type/test bot/arch/x64 bot/channel/nightly bot/platform/macos bot/branch/master | Greetings human!
Bad news. `PlaylistServiceUnitTest.CreateAndRemovePlaylist` [failed on macos x64 nightly master](https://ci.brave.com/job/brave-browser-build-macos-x64-asan/369/testReport/junit/(root)/PlaylistServiceUnitTest/test_unit___CreateAndRemovePlaylist).
<details>
<summary>Stack trace</summary>
```
[ RUN ] PlaylistServiceUnitTest.CreateAndRemovePlaylist
=================================================================
==43573==ERROR: AddressSanitizer: heap-use-after-free on address 0x60700019d288 at pc 0x000111fdfeba bp 0x7ff7be249d50 sp 0x7ff7be249d48
READ of size 8 at 0x60700019d288 thread T0
#0 0x111fdfeb9 in begin buildtools/third_party/libc++/trunk/include/vector:1379:33
#1 0x111fdfeb9 in playlist::PlaylistService::RemovePlaylist(std::Cr::basic_string<char, std::Cr::char_traits<char>, std::Cr::allocator<char>> const&) brave/components/playlist/playlist_service.cc:501:28
#2 0x104cb280e in operator() brave/browser/playlist/test/playlist_service_unittest.cc:583:18
#3 0x104cb280e in base::internal::BindLambdaHelper<playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3, void (std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>)>::Run(playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3 const&, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>) base/test/bind.h:38:12
#4 0x104cb2fe4 in Invoke<void (*const &)(const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > >), const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > > > base/functional/bind_internal.h:536:12
#5 0x104cb2fe4 in MakeItSo<void (*const &)(const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > >), const std::Cr::tuple<(lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7)> &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > > > base/functional/bind_internal.h:825:12
#6 0x104cb2fe4 in RunImpl<void (*const &)(const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > >), const std::Cr::tuple<(lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7)> &, 0UL> base/functional/bind_internal.h:919:12
#7 0x104cb2fe4 in base::internal::Invoker<base::internal::BindState<void (*)(playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3 const&, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>), playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3>, void (std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>)>::Run(base::internal::BindStateBase*, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>&&) base/functional/bind_internal.h:883:12
#8 0x111fd8996 in Run base/functional/callback.h:174:12
#9 0x111fd8996 in playlist::PlaylistService::GetAllPlaylists(base::OnceCallback<void (std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>)>) brave/components/playlist/playlist_service.cc:270:23
#10 0x104c8e37c in playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody() brave/browser/playlist/test/playlist_service_unittest.cc:566:12
#11 0x1121095c3 in testing::Test::Run() third_party/googletest/src/googletest/src/gtest.cc:2670:5
#12 0x11210becd in testing::TestInfo::Run() third_party/googletest/src/googletest/src/gtest.cc:2849:11
#13 0x11210de16 in testing::TestSuite::Run() third_party/googletest/src/googletest/src/gtest.cc:3008:30
#14 0x11213f7e6 in testing::internal::UnitTestImpl::RunAllTests() third_party/googletest/src/googletest/src/gtest.cc:5866:44
#15 0x11213e7fb in testing::UnitTest::Run() third_party/googletest/src/googletest/src/gtest.cc:5440:10
#16 0x1127b9f0d in RUN_ALL_TESTS third_party/googletest/src/googletest/include/gtest/gtest.h:2284:73
#17 0x1127b9f0d in base::TestSuite::Run() base/test/test_suite.cc:445:16
#18 0x112e2202a in content::UnitTestTestSuite::Run() content/public/test/unittest_test_suite.cc:190:23
#19 0x112811813 in Run base/functional/callback.h:174:12
#20 0x112811813 in base::(anonymous namespace)::LaunchUnitTestsInternal(base::OnceCallback<int ()>, unsigned long, int, unsigned long, bool, base::RepeatingCallback<void ()>, base::OnceCallback<void ()>) base/test/launcher/unit_test_launcher.cc:181:38
#21 0x112811425 in base::LaunchUnitTests(int, char**, base::OnceCallback<int ()>, unsigned long) base/test/launcher/unit_test_launcher.cc:272:10
#22 0x112465a5e in main brave/test/base/run_all_unittests.cc:35:10
#23 0x7ff808b5130f (/usr/lib/dyld:x86_64+0xfffffffffff7230f) (BuildId: 28fd207157f3387387bfe4f674a82de632000000200000000100000000000d00)
0x60700019d288 is located 56 bytes inside of 80-byte region [0x60700019d250,0x60700019d2a0)
freed by thread T0 here:
#0 0x14857f9f9 in __asan_memmove (/Users/jenkins/jenkins/workspace/brave-browser-build-macos-x64-asan-nightly/src/out/Release/libclang_rt.asan_osx_dynamic.dylib:x86_64+0x509f9) (BuildId: 4c4c44b055553144a1935d60a83d62722400000010000000000c0a0000030b00)
#1 0x111fdf88c in operator() buildtools/third_party/libc++/trunk/include/__memory/unique_ptr.h:49:5
#2 0x111fdf88c in reset buildtools/third_party/libc++/trunk/include/__memory/unique_ptr.h:281:7
#3 0x111fdf88c in ~unique_ptr buildtools/third_party/libc++/trunk/include/__memory/unique_ptr.h:247:75
#4 0x111fdf88c in ~unique_ptr buildtools/third_party/libc++/trunk/include/__memory/unique_ptr.h:247:73
#5 0x111fdf88c in ~StructPtr mojo/public/cpp/bindings/struct_ptr.h:49:24
#6 0x111fdf88c in ~StructPtr mojo/public/cpp/bindings/struct_ptr.h:49:24
#7 0x111fdf88c in playlist::PlaylistService::RemovePlaylist(std::Cr::basic_string<char, std::Cr::char_traits<char>, std::Cr::allocator<char>> const&) brave/components/playlist/playlist_service.cc:502:10
#8 0x104cb280e in operator() brave/browser/playlist/test/playlist_service_unittest.cc:583:18
#9 0x104cb280e in base::internal::BindLambdaHelper<playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3, void (std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>)>::Run(playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3 const&, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>) base/test/bind.h:38:12
#10 0x104cb2fe4 in Invoke<void (*const &)(const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > >), const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > > > base/functional/bind_internal.h:536:12
#11 0x104cb2fe4 in MakeItSo<void (*const &)(const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > >), const std::Cr::tuple<(lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7)> &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > > > base/functional/bind_internal.h:825:12
#12 0x104cb2fe4 in RunImpl<void (*const &)(const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > >), const std::Cr::tuple<(lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7)> &, 0UL> base/functional/bind_internal.h:919:12
#13 0x104cb2fe4 in base::internal::Invoker<base::internal::BindState<void (*)(playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3 const&, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>), playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3>, void (std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>)>::Run(base::internal::BindStateBase*, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>&&) base/functional/bind_internal.h:883:12
#14 0x111fd8996 in Run base/functional/callback.h:174:12
#15 0x111fd8996 in playlist::PlaylistService::GetAllPlaylists(base::OnceCallback<void (std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>)>) brave/components/playlist/playlist_service.cc:270:23
#16 0x104c8e37c in playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody() brave/browser/playlist/test/playlist_service_unittest.cc:566:12
#17 0x1121095c3 in testing::Test::Run() third_party/googletest/src/googletest/src/gtest.cc:2670:5
#18 0x11210becd in testing::TestInfo::Run() third_party/googletest/src/googletest/src/gtest.cc:2849:11
#19 0x11210de16 in testing::TestSuite::Run() third_party/googletest/src/googletest/src/gtest.cc:3008:30
#20 0x11213f7e6 in testing::internal::UnitTestImpl::RunAllTests() third_party/googletest/src/googletest/src/gtest.cc:5866:44
#21 0x11213e7fb in testing::UnitTest::Run() third_party/googletest/src/googletest/src/gtest.cc:5440:10
#22 0x1127b9f0d in RUN_ALL_TESTS third_party/googletest/src/googletest/include/gtest/gtest.h:2284:73
#23 0x1127b9f0d in base::TestSuite::Run() base/test/test_suite.cc:445:16
#24 0x112e2202a in content::UnitTestTestSuite::Run() content/public/test/unittest_test_suite.cc:190:23
#25 0x112811813 in Run base/functional/callback.h:174:12
#26 0x112811813 in base::(anonymous namespace)::LaunchUnitTestsInternal(base::OnceCallback<int ()>, unsigned long, int, unsigned long, bool, base::RepeatingCallback<void ()>, base::OnceCallback<void ()>) base/test/launcher/unit_test_launcher.cc:181:38
#27 0x112811425 in base::LaunchUnitTests(int, char**, base::OnceCallback<int ()>, unsigned long) base/test/launcher/unit_test_launcher.cc:272:10
#28 0x112465a5e in main brave/test/base/run_all_unittests.cc:35:10
#29 0x7ff808b5130f (/usr/lib/dyld:x86_64+0xfffffffffff7230f) (BuildId: 28fd207157f3387387bfe4f674a82de632000000200000000100000000000d00)
previously allocated by thread T0 here:
#0 0x14857f8b0 in __asan_memmove (/Users/jenkins/jenkins/workspace/brave-browser-build-macos-x64-asan-nightly/src/out/Release/libclang_rt.asan_osx_dynamic.dylib:x86_64+0x508b0) (BuildId: 4c4c44b055553144a1935d60a83d62722400000010000000000c0a0000030b00)
#1 0x1123fad67 in operator new(unsigned long) buildtools/third_party/libc++/trunk/src/new.cpp:67:17
#2 0x111ff2325 in StructPtr<> mojo/public/cpp/bindings/struct_ptr.h:64:14
#3 0x111ff2325 in StructPtr<> mojo/public/cpp/bindings/struct_ptr.h:64:55
#4 0x111ff2325 in New<> /Users/jenkins/jenkins/workspace/brave-browser-build-macos-x64-asan-nightly/src/out/Release/gen/brave/components/playlist/mojom/playlist.mojom.h:527:12
#5 0x111ff2325 in playlist::ConvertValueToPlaylist(base::Value::Dict const&, base::Value::Dict const&) brave/components/playlist/type_converter.cc:98:33
#6 0x111fdf84c in playlist::PlaylistService::RemovePlaylist(std::Cr::basic_string<char, std::Cr::char_traits<char>, std::Cr::allocator<char>> const&) brave/components/playlist/playlist_service.cc:502:10
#7 0x104cb280e in operator() brave/browser/playlist/test/playlist_service_unittest.cc:583:18
#8 0x104cb280e in base::internal::BindLambdaHelper<playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3, void (std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>)>::Run(playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3 const&, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>) base/test/bind.h:38:12
#9 0x104cb2fe4 in Invoke<void (*const &)(const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > >), const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > > > base/functional/bind_internal.h:536:12
#10 0x104cb2fe4 in MakeItSo<void (*const &)(const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > >), const std::Cr::tuple<(lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7)> &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > > > base/functional/bind_internal.h:825:12
#11 0x104cb2fe4 in RunImpl<void (*const &)(const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > >), const std::Cr::tuple<(lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7)> &, 0UL> base/functional/bind_internal.h:919:12
#12 0x104cb2fe4 in base::internal::Invoker<base::internal::BindState<void (*)(playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3 const&, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>), playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3>, void (std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>)>::Run(base::internal::BindStateBase*, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>&&) base/functional/bind_internal.h:883:12
#13 0x111fd8996 in Run base/functional/callback.h:174:12
#14 0x111fd8996 in playlist::PlaylistService::GetAllPlaylists(base::OnceCallback<void (std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>)>) brave/components/playlist/playlist_service.cc:270:23
#15 0x104c8e37c in playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody() brave/browser/playlist/test/playlist_service_unittest.cc:566:12
#16 0x1121095c3 in testing::Test::Run() third_party/googletest/src/googletest/src/gtest.cc:2670:5
#17 0x11210becd in testing::TestInfo::Run() third_party/googletest/src/googletest/src/gtest.cc:2849:11
#18 0x11210de16 in testing::TestSuite::Run() third_party/googletest/src/googletest/src/gtest.cc:3008:30
#19 0x11213f7e6 in testing::internal::UnitTestImpl::RunAllTests() third_party/googletest/src/googletest/src/gtest.cc:5866:44
#20 0x11213e7fb in testing::UnitTest::Run() third_party/googletest/src/googletest/src/gtest.cc:5440:10
#21 0x1127b9f0d in RUN_ALL_TESTS third_party/googletest/src/googletest/include/gtest/gtest.h:2284:73
#22 0x1127b9f0d in base::TestSuite::Run() base/test/test_suite.cc:445:16
#23 0x112e2202a in content::UnitTestTestSuite::Run() content/public/test/unittest_test_suite.cc:190:23
#24 0x112811813 in Run base/functional/callback.h:174:12
#25 0x112811813 in base::(anonymous namespace)::LaunchUnitTestsInternal(base::OnceCallback<int ()>, unsigned long, int, unsigned long, bool, base::RepeatingCallback<void ()>, base::OnceCallback<void ()>) base/test/launcher/unit_test_launcher.cc:181:38
#26 0x112811425 in base::LaunchUnitTests(int, char**, base::OnceCallback<int ()>, unsigned long) base/test/launcher/unit_test_launcher.cc:272:10
#27 0x112465a5e in main brave/test/base/run_all_unittests.cc:35:10
#28 0x7ff808b5130f (/usr/lib/dyld:x86_64+0xfffffffffff7230f) (BuildId: 28fd207157f3387387bfe4f674a82de632000000200000000100000000000d00)
SUMMARY: AddressSanitizer: heap-use-after-free buildtools/third_party/libc++/trunk/include/vector:1379:33 in begin
Shadow bytes around the buggy address:
0x60700019d000: fa fa fa fa fd fd fd fd fd fd fd fd fd fd fa fa
0x60700019d080: fa fa fd fd fd fd fd fd fd fd fd fd fa fa fa fa
0x60700019d100: 00 00 00 00 00 00 00 00 00 00 fa fa fa fa 00 00
0x60700019d180: 00 00 00 00 00 00 00 00 fa fa fa fa fd fd fd fd
0x60700019d200: fd fd fd fd fd fd fa fa fa fa fd fd fd fd fd fd
=>0x60700019d280: fd[fd]fd fd fa fa fa fa fa fa fa fa fa fa fa fa
0x60700019d300: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x60700019d380: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x60700019d400: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x60700019d480: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x60700019d500: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
==43573==ABORTING
Received signal 6
[0x0001126bb872]
[0x00011247f163]
[0x0001126bb5e8]
[0x7ff808eacc1d]
[0x000169326000]
[0x7ff808dcbca5]
[0x0001485a4aa6]
[0x0001485a4204]
[0x000148587e7a]
[0x00014858711d]
[0x000148588428]
[0x000111fdfeba]
[0x000104cb280f]
[0x000104cb2fe5]
[0x000111fd8997]
[0x000104c8e37d]
[0x0001121095c4]
[0x00011210bece]
[0x00011210de17]
[0x00011213f7e7]
[0x00011213e7fc]
[0x0001127b9f0e]
[0x000112e2202b]
[0x000112811814]
[0x000112811426]
[0x000112465a5f]
[0x7ff808b51310]
[end of stack trace]
[ FAILED ] PlaylistServiceUnitTest.CreateAndRemovePlaylist
```
</details>
| 1.0 | Test failure: PlaylistServiceUnitTest.CreateAndRemovePlaylist - Greetings human!
Bad news. `PlaylistServiceUnitTest.CreateAndRemovePlaylist` [failed on macos x64 nightly master](https://ci.brave.com/job/brave-browser-build-macos-x64-asan/369/testReport/junit/(root)/PlaylistServiceUnitTest/test_unit___CreateAndRemovePlaylist).
<details>
<summary>Stack trace</summary>
```
[ RUN ] PlaylistServiceUnitTest.CreateAndRemovePlaylist
=================================================================
==43573==ERROR: AddressSanitizer: heap-use-after-free on address 0x60700019d288 at pc 0x000111fdfeba bp 0x7ff7be249d50 sp 0x7ff7be249d48
READ of size 8 at 0x60700019d288 thread T0
#0 0x111fdfeb9 in begin buildtools/third_party/libc++/trunk/include/vector:1379:33
#1 0x111fdfeb9 in playlist::PlaylistService::RemovePlaylist(std::Cr::basic_string<char, std::Cr::char_traits<char>, std::Cr::allocator<char>> const&) brave/components/playlist/playlist_service.cc:501:28
#2 0x104cb280e in operator() brave/browser/playlist/test/playlist_service_unittest.cc:583:18
#3 0x104cb280e in base::internal::BindLambdaHelper<playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3, void (std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>)>::Run(playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3 const&, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>) base/test/bind.h:38:12
#4 0x104cb2fe4 in Invoke<void (*const &)(const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > >), const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > > > base/functional/bind_internal.h:536:12
#5 0x104cb2fe4 in MakeItSo<void (*const &)(const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > >), const std::Cr::tuple<(lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7)> &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > > > base/functional/bind_internal.h:825:12
#6 0x104cb2fe4 in RunImpl<void (*const &)(const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > >), const std::Cr::tuple<(lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7)> &, 0UL> base/functional/bind_internal.h:919:12
#7 0x104cb2fe4 in base::internal::Invoker<base::internal::BindState<void (*)(playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3 const&, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>), playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3>, void (std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>)>::Run(base::internal::BindStateBase*, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>&&) base/functional/bind_internal.h:883:12
#8 0x111fd8996 in Run base/functional/callback.h:174:12
#9 0x111fd8996 in playlist::PlaylistService::GetAllPlaylists(base::OnceCallback<void (std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>)>) brave/components/playlist/playlist_service.cc:270:23
#10 0x104c8e37c in playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody() brave/browser/playlist/test/playlist_service_unittest.cc:566:12
#11 0x1121095c3 in testing::Test::Run() third_party/googletest/src/googletest/src/gtest.cc:2670:5
#12 0x11210becd in testing::TestInfo::Run() third_party/googletest/src/googletest/src/gtest.cc:2849:11
#13 0x11210de16 in testing::TestSuite::Run() third_party/googletest/src/googletest/src/gtest.cc:3008:30
#14 0x11213f7e6 in testing::internal::UnitTestImpl::RunAllTests() third_party/googletest/src/googletest/src/gtest.cc:5866:44
#15 0x11213e7fb in testing::UnitTest::Run() third_party/googletest/src/googletest/src/gtest.cc:5440:10
#16 0x1127b9f0d in RUN_ALL_TESTS third_party/googletest/src/googletest/include/gtest/gtest.h:2284:73
#17 0x1127b9f0d in base::TestSuite::Run() base/test/test_suite.cc:445:16
#18 0x112e2202a in content::UnitTestTestSuite::Run() content/public/test/unittest_test_suite.cc:190:23
#19 0x112811813 in Run base/functional/callback.h:174:12
#20 0x112811813 in base::(anonymous namespace)::LaunchUnitTestsInternal(base::OnceCallback<int ()>, unsigned long, int, unsigned long, bool, base::RepeatingCallback<void ()>, base::OnceCallback<void ()>) base/test/launcher/unit_test_launcher.cc:181:38
#21 0x112811425 in base::LaunchUnitTests(int, char**, base::OnceCallback<int ()>, unsigned long) base/test/launcher/unit_test_launcher.cc:272:10
#22 0x112465a5e in main brave/test/base/run_all_unittests.cc:35:10
#23 0x7ff808b5130f (/usr/lib/dyld:x86_64+0xfffffffffff7230f) (BuildId: 28fd207157f3387387bfe4f674a82de632000000200000000100000000000d00)
0x60700019d288 is located 56 bytes inside of 80-byte region [0x60700019d250,0x60700019d2a0)
freed by thread T0 here:
#0 0x14857f9f9 in __asan_memmove (/Users/jenkins/jenkins/workspace/brave-browser-build-macos-x64-asan-nightly/src/out/Release/libclang_rt.asan_osx_dynamic.dylib:x86_64+0x509f9) (BuildId: 4c4c44b055553144a1935d60a83d62722400000010000000000c0a0000030b00)
#1 0x111fdf88c in operator() buildtools/third_party/libc++/trunk/include/__memory/unique_ptr.h:49:5
#2 0x111fdf88c in reset buildtools/third_party/libc++/trunk/include/__memory/unique_ptr.h:281:7
#3 0x111fdf88c in ~unique_ptr buildtools/third_party/libc++/trunk/include/__memory/unique_ptr.h:247:75
#4 0x111fdf88c in ~unique_ptr buildtools/third_party/libc++/trunk/include/__memory/unique_ptr.h:247:73
#5 0x111fdf88c in ~StructPtr mojo/public/cpp/bindings/struct_ptr.h:49:24
#6 0x111fdf88c in ~StructPtr mojo/public/cpp/bindings/struct_ptr.h:49:24
#7 0x111fdf88c in playlist::PlaylistService::RemovePlaylist(std::Cr::basic_string<char, std::Cr::char_traits<char>, std::Cr::allocator<char>> const&) brave/components/playlist/playlist_service.cc:502:10
#8 0x104cb280e in operator() brave/browser/playlist/test/playlist_service_unittest.cc:583:18
#9 0x104cb280e in base::internal::BindLambdaHelper<playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3, void (std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>)>::Run(playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3 const&, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>) base/test/bind.h:38:12
#10 0x104cb2fe4 in Invoke<void (*const &)(const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > >), const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > > > base/functional/bind_internal.h:536:12
#11 0x104cb2fe4 in MakeItSo<void (*const &)(const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > >), const std::Cr::tuple<(lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7)> &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > > > base/functional/bind_internal.h:825:12
#12 0x104cb2fe4 in RunImpl<void (*const &)(const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > >), const std::Cr::tuple<(lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7)> &, 0UL> base/functional/bind_internal.h:919:12
#13 0x104cb2fe4 in base::internal::Invoker<base::internal::BindState<void (*)(playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3 const&, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>), playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3>, void (std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>)>::Run(base::internal::BindStateBase*, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>&&) base/functional/bind_internal.h:883:12
#14 0x111fd8996 in Run base/functional/callback.h:174:12
#15 0x111fd8996 in playlist::PlaylistService::GetAllPlaylists(base::OnceCallback<void (std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>)>) brave/components/playlist/playlist_service.cc:270:23
#16 0x104c8e37c in playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody() brave/browser/playlist/test/playlist_service_unittest.cc:566:12
#17 0x1121095c3 in testing::Test::Run() third_party/googletest/src/googletest/src/gtest.cc:2670:5
#18 0x11210becd in testing::TestInfo::Run() third_party/googletest/src/googletest/src/gtest.cc:2849:11
#19 0x11210de16 in testing::TestSuite::Run() third_party/googletest/src/googletest/src/gtest.cc:3008:30
#20 0x11213f7e6 in testing::internal::UnitTestImpl::RunAllTests() third_party/googletest/src/googletest/src/gtest.cc:5866:44
#21 0x11213e7fb in testing::UnitTest::Run() third_party/googletest/src/googletest/src/gtest.cc:5440:10
#22 0x1127b9f0d in RUN_ALL_TESTS third_party/googletest/src/googletest/include/gtest/gtest.h:2284:73
#23 0x1127b9f0d in base::TestSuite::Run() base/test/test_suite.cc:445:16
#24 0x112e2202a in content::UnitTestTestSuite::Run() content/public/test/unittest_test_suite.cc:190:23
#25 0x112811813 in Run base/functional/callback.h:174:12
#26 0x112811813 in base::(anonymous namespace)::LaunchUnitTestsInternal(base::OnceCallback<int ()>, unsigned long, int, unsigned long, bool, base::RepeatingCallback<void ()>, base::OnceCallback<void ()>) base/test/launcher/unit_test_launcher.cc:181:38
#27 0x112811425 in base::LaunchUnitTests(int, char**, base::OnceCallback<int ()>, unsigned long) base/test/launcher/unit_test_launcher.cc:272:10
#28 0x112465a5e in main brave/test/base/run_all_unittests.cc:35:10
#29 0x7ff808b5130f (/usr/lib/dyld:x86_64+0xfffffffffff7230f) (BuildId: 28fd207157f3387387bfe4f674a82de632000000200000000100000000000d00)
previously allocated by thread T0 here:
#0 0x14857f8b0 in __asan_memmove (/Users/jenkins/jenkins/workspace/brave-browser-build-macos-x64-asan-nightly/src/out/Release/libclang_rt.asan_osx_dynamic.dylib:x86_64+0x508b0) (BuildId: 4c4c44b055553144a1935d60a83d62722400000010000000000c0a0000030b00)
#1 0x1123fad67 in operator new(unsigned long) buildtools/third_party/libc++/trunk/src/new.cpp:67:17
#2 0x111ff2325 in StructPtr<> mojo/public/cpp/bindings/struct_ptr.h:64:14
#3 0x111ff2325 in StructPtr<> mojo/public/cpp/bindings/struct_ptr.h:64:55
#4 0x111ff2325 in New<> /Users/jenkins/jenkins/workspace/brave-browser-build-macos-x64-asan-nightly/src/out/Release/gen/brave/components/playlist/mojom/playlist.mojom.h:527:12
#5 0x111ff2325 in playlist::ConvertValueToPlaylist(base::Value::Dict const&, base::Value::Dict const&) brave/components/playlist/type_converter.cc:98:33
#6 0x111fdf84c in playlist::PlaylistService::RemovePlaylist(std::Cr::basic_string<char, std::Cr::char_traits<char>, std::Cr::allocator<char>> const&) brave/components/playlist/playlist_service.cc:502:10
#7 0x104cb280e in operator() brave/browser/playlist/test/playlist_service_unittest.cc:583:18
#8 0x104cb280e in base::internal::BindLambdaHelper<playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3, void (std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>)>::Run(playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3 const&, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>) base/test/bind.h:38:12
#9 0x104cb2fe4 in Invoke<void (*const &)(const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > >), const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > > > base/functional/bind_internal.h:536:12
#10 0x104cb2fe4 in MakeItSo<void (*const &)(const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > >), const std::Cr::tuple<(lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7)> &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > > > base/functional/bind_internal.h:825:12
#11 0x104cb2fe4 in RunImpl<void (*const &)(const (lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7) &, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist> > >), const std::Cr::tuple<(lambda at ../../brave/browser/playlist/test/playlist_service_unittest.cc:567:7)> &, 0UL> base/functional/bind_internal.h:919:12
#12 0x104cb2fe4 in base::internal::Invoker<base::internal::BindState<void (*)(playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3 const&, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>), playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody()::$_3>, void (std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>)>::Run(base::internal::BindStateBase*, std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>&&) base/functional/bind_internal.h:883:12
#13 0x111fd8996 in Run base/functional/callback.h:174:12
#14 0x111fd8996 in playlist::PlaylistService::GetAllPlaylists(base::OnceCallback<void (std::Cr::vector<mojo::StructPtr<playlist::mojom::Playlist>, std::Cr::allocator<mojo::StructPtr<playlist::mojom::Playlist>>>)>) brave/components/playlist/playlist_service.cc:270:23
#15 0x104c8e37c in playlist::PlaylistServiceUnitTest_CreateAndRemovePlaylist_Test::TestBody() brave/browser/playlist/test/playlist_service_unittest.cc:566:12
#16 0x1121095c3 in testing::Test::Run() third_party/googletest/src/googletest/src/gtest.cc:2670:5
#17 0x11210becd in testing::TestInfo::Run() third_party/googletest/src/googletest/src/gtest.cc:2849:11
#18 0x11210de16 in testing::TestSuite::Run() third_party/googletest/src/googletest/src/gtest.cc:3008:30
#19 0x11213f7e6 in testing::internal::UnitTestImpl::RunAllTests() third_party/googletest/src/googletest/src/gtest.cc:5866:44
#20 0x11213e7fb in testing::UnitTest::Run() third_party/googletest/src/googletest/src/gtest.cc:5440:10
#21 0x1127b9f0d in RUN_ALL_TESTS third_party/googletest/src/googletest/include/gtest/gtest.h:2284:73
#22 0x1127b9f0d in base::TestSuite::Run() base/test/test_suite.cc:445:16
#23 0x112e2202a in content::UnitTestTestSuite::Run() content/public/test/unittest_test_suite.cc:190:23
#24 0x112811813 in Run base/functional/callback.h:174:12
#25 0x112811813 in base::(anonymous namespace)::LaunchUnitTestsInternal(base::OnceCallback<int ()>, unsigned long, int, unsigned long, bool, base::RepeatingCallback<void ()>, base::OnceCallback<void ()>) base/test/launcher/unit_test_launcher.cc:181:38
#26 0x112811425 in base::LaunchUnitTests(int, char**, base::OnceCallback<int ()>, unsigned long) base/test/launcher/unit_test_launcher.cc:272:10
#27 0x112465a5e in main brave/test/base/run_all_unittests.cc:35:10
#28 0x7ff808b5130f (/usr/lib/dyld:x86_64+0xfffffffffff7230f) (BuildId: 28fd207157f3387387bfe4f674a82de632000000200000000100000000000d00)
SUMMARY: AddressSanitizer: heap-use-after-free buildtools/third_party/libc++/trunk/include/vector:1379:33 in begin
Shadow bytes around the buggy address:
0x60700019d000: fa fa fa fa fd fd fd fd fd fd fd fd fd fd fa fa
0x60700019d080: fa fa fd fd fd fd fd fd fd fd fd fd fa fa fa fa
0x60700019d100: 00 00 00 00 00 00 00 00 00 00 fa fa fa fa 00 00
0x60700019d180: 00 00 00 00 00 00 00 00 fa fa fa fa fd fd fd fd
0x60700019d200: fd fd fd fd fd fd fa fa fa fa fd fd fd fd fd fd
=>0x60700019d280: fd[fd]fd fd fa fa fa fa fa fa fa fa fa fa fa fa
0x60700019d300: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x60700019d380: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x60700019d400: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x60700019d480: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x60700019d500: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
==43573==ABORTING
Received signal 6
[0x0001126bb872]
[0x00011247f163]
[0x0001126bb5e8]
[0x7ff808eacc1d]
[0x000169326000]
[0x7ff808dcbca5]
[0x0001485a4aa6]
[0x0001485a4204]
[0x000148587e7a]
[0x00014858711d]
[0x000148588428]
[0x000111fdfeba]
[0x000104cb280f]
[0x000104cb2fe5]
[0x000111fd8997]
[0x000104c8e37d]
[0x0001121095c4]
[0x00011210bece]
[0x00011210de17]
[0x00011213f7e7]
[0x00011213e7fc]
[0x0001127b9f0e]
[0x000112e2202b]
[0x000112811814]
[0x000112811426]
[0x000112465a5f]
[0x7ff808b51310]
[end of stack trace]
[ FAILED ] PlaylistServiceUnitTest.CreateAndRemovePlaylist
```
</details>
| non_priority | test failure playlistserviceunittest createandremoveplaylist greetings human bad news playlistserviceunittest createandremoveplaylist stack trace playlistserviceunittest createandremoveplaylist error addresssanitizer heap use after free on address at pc bp sp read of size at thread in begin buildtools third party libc trunk include vector in playlist playlistservice removeplaylist std cr basic string std cr allocator const brave components playlist playlist service cc in operator brave browser playlist test playlist service unittest cc in base internal bindlambdahelper std cr allocator run playlist playlistserviceunittest createandremoveplaylist test testbody const std cr vector std cr allocator base test bind h in invoke std cr allocator const lambda at brave browser playlist test playlist service unittest cc std cr vector std cr allocator base functional bind internal h in makeitso std cr allocator const std cr tuple std cr vector std cr allocator base functional bind internal h in runimpl std cr allocator const std cr tuple base functional bind internal h in base internal invoker std cr allocator playlist playlistserviceunittest createandremoveplaylist test testbody void std cr vector std cr allocator run base internal bindstatebase std cr vector std cr allocator base functional bind internal h in run base functional callback h in playlist playlistservice getallplaylists base oncecallback std cr allocator brave components playlist playlist service cc in playlist playlistserviceunittest createandremoveplaylist test testbody brave browser playlist test playlist service unittest cc in testing test run third party googletest src googletest src gtest cc in testing testinfo run third party googletest src googletest src gtest cc in testing testsuite run third party googletest src googletest src gtest cc in testing internal unittestimpl runalltests third party googletest src googletest src gtest cc in testing unittest run third party googletest src googletest src gtest cc in run all tests third party googletest src googletest include gtest gtest h in base testsuite run base test test suite cc in content unittesttestsuite run content public test unittest test suite cc in run base functional callback h in base anonymous namespace launchunittestsinternal base oncecallback unsigned long int unsigned long bool base repeatingcallback base oncecallback base test launcher unit test launcher cc in base launchunittests int char base oncecallback unsigned long base test launcher unit test launcher cc in main brave test base run all unittests cc usr lib dyld buildid is located bytes inside of byte region freed by thread here in asan memmove users jenkins jenkins workspace brave browser build macos asan nightly src out release libclang rt asan osx dynamic dylib buildid in operator buildtools third party libc trunk include memory unique ptr h in reset buildtools third party libc trunk include memory unique ptr h in unique ptr buildtools third party libc trunk include memory unique ptr h in unique ptr buildtools third party libc trunk include memory unique ptr h in structptr mojo public cpp bindings struct ptr h in structptr mojo public cpp bindings struct ptr h in playlist playlistservice removeplaylist std cr basic string std cr allocator const brave components playlist playlist service cc in operator brave browser playlist test playlist service unittest cc in base internal bindlambdahelper std cr allocator run playlist playlistserviceunittest createandremoveplaylist test testbody const std cr vector std cr allocator base test bind h in invoke std cr allocator const lambda at brave browser playlist test playlist service unittest cc std cr vector std cr allocator base functional bind internal h in makeitso std cr allocator const std cr tuple std cr vector std cr allocator base functional bind internal h in runimpl std cr allocator const std cr tuple base functional bind internal h in base internal invoker std cr allocator playlist playlistserviceunittest createandremoveplaylist test testbody void std cr vector std cr allocator run base internal bindstatebase std cr vector std cr allocator base functional bind internal h in run base functional callback h in playlist playlistservice getallplaylists base oncecallback std cr allocator brave components playlist playlist service cc in playlist playlistserviceunittest createandremoveplaylist test testbody brave browser playlist test playlist service unittest cc in testing test run third party googletest src googletest src gtest cc in testing testinfo run third party googletest src googletest src gtest cc in testing testsuite run third party googletest src googletest src gtest cc in testing internal unittestimpl runalltests third party googletest src googletest src gtest cc in testing unittest run third party googletest src googletest src gtest cc in run all tests third party googletest src googletest include gtest gtest h in base testsuite run base test test suite cc in content unittesttestsuite run content public test unittest test suite cc in run base functional callback h in base anonymous namespace launchunittestsinternal base oncecallback unsigned long int unsigned long bool base repeatingcallback base oncecallback base test launcher unit test launcher cc in base launchunittests int char base oncecallback unsigned long base test launcher unit test launcher cc in main brave test base run all unittests cc usr lib dyld buildid previously allocated by thread here in asan memmove users jenkins jenkins workspace brave browser build macos asan nightly src out release libclang rt asan osx dynamic dylib buildid in operator new unsigned long buildtools third party libc trunk src new cpp in structptr mojo public cpp bindings struct ptr h in structptr mojo public cpp bindings struct ptr h in new users jenkins jenkins workspace brave browser build macos asan nightly src out release gen brave components playlist mojom playlist mojom h in playlist convertvaluetoplaylist base value dict const base value dict const brave components playlist type converter cc in playlist playlistservice removeplaylist std cr basic string std cr allocator const brave components playlist playlist service cc in operator brave browser playlist test playlist service unittest cc in base internal bindlambdahelper std cr allocator run playlist playlistserviceunittest createandremoveplaylist test testbody const std cr vector std cr allocator base test bind h in invoke std cr allocator const lambda at brave browser playlist test playlist service unittest cc std cr vector std cr allocator base functional bind internal h in makeitso std cr allocator const std cr tuple std cr vector std cr allocator base functional bind internal h in runimpl std cr allocator const std cr tuple base functional bind internal h in base internal invoker std cr allocator playlist playlistserviceunittest createandremoveplaylist test testbody void std cr vector std cr allocator run base internal bindstatebase std cr vector std cr allocator base functional bind internal h in run base functional callback h in playlist playlistservice getallplaylists base oncecallback std cr allocator brave components playlist playlist service cc in playlist playlistserviceunittest createandremoveplaylist test testbody brave browser playlist test playlist service unittest cc in testing test run third party googletest src googletest src gtest cc in testing testinfo run third party googletest src googletest src gtest cc in testing testsuite run third party googletest src googletest src gtest cc in testing internal unittestimpl runalltests third party googletest src googletest src gtest cc in testing unittest run third party googletest src googletest src gtest cc in run all tests third party googletest src googletest include gtest gtest h in base testsuite run base test test suite cc in content unittesttestsuite run content public test unittest test suite cc in run base functional callback h in base anonymous namespace launchunittestsinternal base oncecallback unsigned long int unsigned long bool base repeatingcallback base oncecallback base test launcher unit test launcher cc in base launchunittests int char base oncecallback unsigned long base test launcher unit test launcher cc in main brave test base run all unittests cc usr lib dyld buildid summary addresssanitizer heap use after free buildtools third party libc trunk include vector in begin shadow bytes around the buggy address fa fa fa fa fd fd fd fd fd fd fd fd fd fd fa fa fa fa fd fd fd fd fd fd fd fd fd fd fa fa fa fa fa fa fa fa fa fa fa fa fd fd fd fd fd fd fd fd fd fd fa fa fa fa fd fd fd fd fd fd fd fd fd fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa shadow byte legend one shadow byte represents application bytes addressable partially addressable heap left redzone fa freed heap region fd stack left redzone stack mid redzone stack right redzone stack after return stack use after scope global redzone global init order poisoned by user container overflow fc array cookie ac intra object redzone bb asan internal fe left alloca redzone ca right alloca redzone cb aborting received signal playlistserviceunittest createandremoveplaylist | 0 |
180,205 | 14,741,659,630 | IssuesEvent | 2021-01-07 10:58:01 | sangwoo-98/Study | https://api.github.com/repos/sangwoo-98/Study | reopened | 정리할 것 | documentation | - [x] RuntimeException과 Exception 차이
- [x] @ResponseStatus의 사용
- [x] @Valid, @notblank, @ValueOfEnum의 사용 | 1.0 | 정리할 것 - - [x] RuntimeException과 Exception 차이
- [x] @ResponseStatus의 사용
- [x] @Valid, @notblank, @ValueOfEnum의 사용 | non_priority | 정리할 것 runtimeexception과 exception 차이 responsestatus의 사용 valid notblank valueofenum의 사용 | 0 |
84,280 | 24,269,087,518 | IssuesEvent | 2022-09-28 08:52:07 | shengnoah/secbooks.cn | https://api.github.com/repos/shengnoah/secbooks.cn | opened | Build arguments | Gitalk /mydoc_build_arguments.html | https://secbooks.cn/mydoc_build_arguments.html
You use various build arguments with your Jekyll project. You can also create shell scripts to act as shortcuts for long build commands. You can store the co... | 1.0 | Build arguments - https://secbooks.cn/mydoc_build_arguments.html
You use various build arguments with your Jekyll project. You can also create shell scripts to act as shortcuts for long build commands. You can store the co... | non_priority | build arguments you use various build arguments with your jekyll project you can also create shell scripts to act as shortcuts for long build commands you can store the co | 0 |
86,836 | 24,968,143,529 | IssuesEvent | 2022-11-01 21:22:42 | TEAM-AAAAAAAAAAAAAAAA/RTYPE | https://api.github.com/repos/TEAM-AAAAAAAAAAAAAAAA/RTYPE | opened | BUILD - use `target_source` for headers files | BUILD ECS | - Use cmakes `target_source` for installing headers as part of a target | 1.0 | BUILD - use `target_source` for headers files - - Use cmakes `target_source` for installing headers as part of a target | non_priority | build use target source for headers files use cmakes target source for installing headers as part of a target | 0 |
233,873 | 25,780,402,826 | IssuesEvent | 2022-12-09 15:26:54 | smb-h/Estates-price-prediction | https://api.github.com/repos/smb-h/Estates-price-prediction | closed | CVE-2022-36013 (High) detected in tensorflow-2.6.3-cp37-cp37m-manylinux2010_x86_64.whl | security vulnerability | ## CVE-2022-36013 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-2.6.3-cp37-cp37m-manylinux2010_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/73/a3/142f73d0e076f5582fd8da29c68af0413bf529933eed09f86a8857fab0d6/tensorflow-2.6.3-cp37-cp37m-manylinux2010_x86_64.whl">https://files.pythonhosted.org/packages/73/a3/142f73d0e076f5582fd8da29c68af0413bf529933eed09f86a8857fab0d6/tensorflow-2.6.3-cp37-cp37m-manylinux2010_x86_64.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-2.6.3-cp37-cp37m-manylinux2010_x86_64.whl** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an open source platform for machine learning. When `mlir::tfg::GraphDefImporter::ConvertNodeDef` tries to convert NodeDefs without an op name, it crashes. We have patched the issue in GitHub commit a0f0b9a21c9270930457095092f558fbad4c03e5. The fix will be included in TensorFlow 2.10.0. We will also cherrypick this commit on TensorFlow 2.9.1, TensorFlow 2.8.1, and TensorFlow 2.7.2, as these are also affected and still in supported range. There are no known workarounds for this issue.
<p>Publish Date: 2022-09-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-36013>CVE-2022-36013</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-828c-5j5q-vrjq">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-828c-5j5q-vrjq</a></p>
<p>Release Date: 2022-09-16</p>
<p>Fix Resolution: tensorflow - 2.7.2,2.8.1,2.9.1,2.10.0, tensorflow-cpu - 2.7.2,2.8.1,2.9.1,2.10.0, tensorflow-gpu - 2.7.2,2.8.1,2.9.1,2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-36013 (High) detected in tensorflow-2.6.3-cp37-cp37m-manylinux2010_x86_64.whl - ## CVE-2022-36013 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-2.6.3-cp37-cp37m-manylinux2010_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/73/a3/142f73d0e076f5582fd8da29c68af0413bf529933eed09f86a8857fab0d6/tensorflow-2.6.3-cp37-cp37m-manylinux2010_x86_64.whl">https://files.pythonhosted.org/packages/73/a3/142f73d0e076f5582fd8da29c68af0413bf529933eed09f86a8857fab0d6/tensorflow-2.6.3-cp37-cp37m-manylinux2010_x86_64.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-2.6.3-cp37-cp37m-manylinux2010_x86_64.whl** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an open source platform for machine learning. When `mlir::tfg::GraphDefImporter::ConvertNodeDef` tries to convert NodeDefs without an op name, it crashes. We have patched the issue in GitHub commit a0f0b9a21c9270930457095092f558fbad4c03e5. The fix will be included in TensorFlow 2.10.0. We will also cherrypick this commit on TensorFlow 2.9.1, TensorFlow 2.8.1, and TensorFlow 2.7.2, as these are also affected and still in supported range. There are no known workarounds for this issue.
<p>Publish Date: 2022-09-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-36013>CVE-2022-36013</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-828c-5j5q-vrjq">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-828c-5j5q-vrjq</a></p>
<p>Release Date: 2022-09-16</p>
<p>Fix Resolution: tensorflow - 2.7.2,2.8.1,2.9.1,2.10.0, tensorflow-cpu - 2.7.2,2.8.1,2.9.1,2.10.0, tensorflow-gpu - 2.7.2,2.8.1,2.9.1,2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in tensorflow whl cve high severity vulnerability vulnerable library tensorflow whl tensorflow is an open source machine learning framework for everyone library home page a href path to dependency file requirements txt path to vulnerable library requirements txt dependency hierarchy x tensorflow whl vulnerable library found in base branch main vulnerability details tensorflow is an open source platform for machine learning when mlir tfg graphdefimporter convertnodedef tries to convert nodedefs without an op name it crashes we have patched the issue in github commit the fix will be included in tensorflow we will also cherrypick this commit on tensorflow tensorflow and tensorflow as these are also affected and still in supported range there are no known workarounds for this issue publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tensorflow tensorflow cpu tensorflow gpu step up your open source security game with mend | 0 |
30,760 | 25,044,411,880 | IssuesEvent | 2022-11-05 03:50:02 | UBCSailbot/docs | https://api.github.com/repos/UBCSailbot/docs | closed | Make Hyperlinks Open a New Tab | infrastructure | ### Purpose
Change hyperlinks on pages to open a new tab rather than navigate to a new page away from the docs website. Only do this for external sites.
### Changes
1. If the hyperlink is to an external site, then add `{target=_blank}` to the end of the link. For example:
```
[Python Tutorial](https://docs.python.org/3/tutorial/){target=_blank}
```
2. If the hyperlink is to another page on the docs site, then **leave it be**.
| 1.0 | Make Hyperlinks Open a New Tab - ### Purpose
Change hyperlinks on pages to open a new tab rather than navigate to a new page away from the docs website. Only do this for external sites.
### Changes
1. If the hyperlink is to an external site, then add `{target=_blank}` to the end of the link. For example:
```
[Python Tutorial](https://docs.python.org/3/tutorial/){target=_blank}
```
2. If the hyperlink is to another page on the docs site, then **leave it be**.
| non_priority | make hyperlinks open a new tab purpose change hyperlinks on pages to open a new tab rather than navigate to a new page away from the docs website only do this for external sites changes if the hyperlink is to an external site then add target blank to the end of the link for example if the hyperlink is to another page on the docs site then leave it be | 0 |
427,825 | 29,865,120,086 | IssuesEvent | 2023-06-20 02:38:14 | apache/arrow | https://api.github.com/repos/apache/arrow | closed | [Docs][Parquet] Document Parquet implementation status | Type: enhancement Component: Documentation | ### Describe the enhancement requested
There is no comprehensive documentation on the publicly available parquet features. The docs of different parquet featuers are scattered across different repositories and their issue queues. Related note: https://github.com/apache/arrow/issues/35638#issuecomment-1584966456
### Component(s)
Documentation | 1.0 | [Docs][Parquet] Document Parquet implementation status - ### Describe the enhancement requested
There is no comprehensive documentation on the publicly available parquet features. The docs of different parquet featuers are scattered across different repositories and their issue queues. Related note: https://github.com/apache/arrow/issues/35638#issuecomment-1584966456
### Component(s)
Documentation | non_priority | document parquet implementation status describe the enhancement requested there is no comprehensive documentation on the publicly available parquet features the docs of different parquet featuers are scattered across different repositories and their issue queues related note component s documentation | 0 |
106,214 | 13,255,750,881 | IssuesEvent | 2020-08-20 11:30:30 | ant-design/pro-components | https://api.github.com/repos/ant-design/pro-components | closed | 🧐[问题]valueType=dateRange的疑问 | table 🎨 By Design | ### 🧐 问题描述
以前的用法就是查询表单可以选择查询某个时间端的数据,这在我这里算是正常的业务逻辑,现在新版本的居然变成了表格中的数据也展示成一个区间,这是什么业务才有的数据展现模式,非常不理解为什么要改成这样!!
### 💻 示例代码
<!--
如果你有解决方案,在这里清晰地阐述
-->
### 🚑 其他信息
<!--
如截图等其他信息可以贴在这里
-->
| 1.0 | 🧐[问题]valueType=dateRange的疑问 - ### 🧐 问题描述
以前的用法就是查询表单可以选择查询某个时间端的数据,这在我这里算是正常的业务逻辑,现在新版本的居然变成了表格中的数据也展示成一个区间,这是什么业务才有的数据展现模式,非常不理解为什么要改成这样!!
### 💻 示例代码
<!--
如果你有解决方案,在这里清晰地阐述
-->
### 🚑 其他信息
<!--
如截图等其他信息可以贴在这里
-->
| non_priority | 🧐 valuetype daterange的疑问 🧐 问题描述 以前的用法就是查询表单可以选择查询某个时间端的数据,这在我这里算是正常的业务逻辑,现在新版本的居然变成了表格中的数据也展示成一个区间,这是什么业务才有的数据展现模式,非常不理解为什么要改成这样!! 💻 示例代码 如果你有解决方案,在这里清晰地阐述 🚑 其他信息 如截图等其他信息可以贴在这里 | 0 |
199,854 | 15,079,781,404 | IssuesEvent | 2021-02-05 10:38:23 | Paul2497/Opensource-Bug-Reporting | https://api.github.com/repos/Paul2497/Opensource-Bug-Reporting | opened | Admin Dashboard: The remaining percentage data was not displayed in Employee Distribution by Subunit [Pie Chart] | Enhancement Test p-Low | 
| 1.0 | Admin Dashboard: The remaining percentage data was not displayed in Employee Distribution by Subunit [Pie Chart] - 
| non_priority | admin dashboard the remaining percentage data was not displayed in employee distribution by subunit | 0 |
340,608 | 30,530,470,969 | IssuesEvent | 2023-07-19 14:00:23 | WPChill/strong-testimonials | https://api.github.com/repos/WPChill/strong-testimonials | closed | manual excerpts are not displayed | bug need testing | **Describe the bug**
We had a big update from Wordpress 5 to the latest. You can see the problem on my dutch Homepage linkpizza.com/nl and we use the last Elementor Pro. 1. The Excerpt isn't showing in all the views. The testimonals had only Name, Company name and the excerpt. I Just filled the content in excerpt also in the normal content. 2. Then its showing. But the text of the normal content is overlapping by the picture on desktop. On Mobile its not a problem.
1. This is what happens with the normal content filled.

2. This is what happens with only Excerpt filled.

https://secure.helpscout.net/conversation/2273096157/57858?folderId=4656052
#### Used versions
* WordPress version: 6.2.2
* Strong Testimonials version: 3.1.7
| 1.0 | manual excerpts are not displayed - **Describe the bug**
We had a big update from Wordpress 5 to the latest. You can see the problem on my dutch Homepage linkpizza.com/nl and we use the last Elementor Pro. 1. The Excerpt isn't showing in all the views. The testimonals had only Name, Company name and the excerpt. I Just filled the content in excerpt also in the normal content. 2. Then its showing. But the text of the normal content is overlapping by the picture on desktop. On Mobile its not a problem.
1. This is what happens with the normal content filled.

2. This is what happens with only Excerpt filled.

https://secure.helpscout.net/conversation/2273096157/57858?folderId=4656052
#### Used versions
* WordPress version: 6.2.2
* Strong Testimonials version: 3.1.7
| non_priority | manual excerpts are not displayed describe the bug we had a big update from wordpress to the latest you can see the problem on my dutch homepage linkpizza com nl and we use the last elementor pro the excerpt isn t showing in all the views the testimonals had only name company name and the excerpt i just filled the content in excerpt also in the normal content then its showing but the text of the normal content is overlapping by the picture on desktop on mobile its not a problem this is what happens with the normal content filled this is what happens with only excerpt filled used versions wordpress version strong testimonials version | 0 |
41,729 | 9,037,657,780 | IssuesEvent | 2019-02-09 12:58:27 | ThosRTanner/inforss | https://api.github.com/repos/ThosRTanner/inforss | closed | Refactor feed handlers | Code cleanup | Really the base should be responsible for adding properly formatted headlines to the headline bar. However, currently there's at least 3 different ways of doing this as the abstraction is at the wrong level.
Refactor the code so that the individual feed handlers build a list of headlines then the base feed handler adds/removes each headline the child detects to the main display.
Also note that for atom and rss feeds the publication date doesn't need a horrendous regex to determine the correct date. Possibly nntp feeds too. | 1.0 | Refactor feed handlers - Really the base should be responsible for adding properly formatted headlines to the headline bar. However, currently there's at least 3 different ways of doing this as the abstraction is at the wrong level.
Refactor the code so that the individual feed handlers build a list of headlines then the base feed handler adds/removes each headline the child detects to the main display.
Also note that for atom and rss feeds the publication date doesn't need a horrendous regex to determine the correct date. Possibly nntp feeds too. | non_priority | refactor feed handlers really the base should be responsible for adding properly formatted headlines to the headline bar however currently there s at least different ways of doing this as the abstraction is at the wrong level refactor the code so that the individual feed handlers build a list of headlines then the base feed handler adds removes each headline the child detects to the main display also note that for atom and rss feeds the publication date doesn t need a horrendous regex to determine the correct date possibly nntp feeds too | 0 |
130,310 | 18,063,632,757 | IssuesEvent | 2021-09-20 16:28:01 | WordPress/gutenberg | https://api.github.com/repos/WordPress/gutenberg | closed | Squiggly line looks like spelling mistake not link in interface | [Status] In Progress Needs Design Feedback [Block] Navigation Link | I 'think' the squiggly line indicates that the navigation is a link, but typically a wiggly line would indicate that something, for example, might be a spelling mistake or problem, not that it's a link.

I would recommend that another visual is used in this case, even going back to having an underline as the wiggly line means a mistake and could easily get read as that here. Whilst typically the 'error' underline squiggly is also red, it feels just too similar to be used to mean link. I also might totally have it wrong what this is meant to mean, though.
| 1.0 | Squiggly line looks like spelling mistake not link in interface - I 'think' the squiggly line indicates that the navigation is a link, but typically a wiggly line would indicate that something, for example, might be a spelling mistake or problem, not that it's a link.

I would recommend that another visual is used in this case, even going back to having an underline as the wiggly line means a mistake and could easily get read as that here. Whilst typically the 'error' underline squiggly is also red, it feels just too similar to be used to mean link. I also might totally have it wrong what this is meant to mean, though.
| non_priority | squiggly line looks like spelling mistake not link in interface i think the squiggly line indicates that the navigation is a link but typically a wiggly line would indicate that something for example might be a spelling mistake or problem not that it s a link i would recommend that another visual is used in this case even going back to having an underline as the wiggly line means a mistake and could easily get read as that here whilst typically the error underline squiggly is also red it feels just too similar to be used to mean link i also might totally have it wrong what this is meant to mean though | 0 |
77,176 | 15,499,646,522 | IssuesEvent | 2021-03-11 08:15:34 | averageflow/goscope | https://api.github.com/repos/averageflow/goscope | closed | CVE-2020-28168 (Medium) detected in axios-0.19.2.tgz | security vulnerability | ## CVE-2020-28168 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>axios-0.19.2.tgz</b></p></summary>
<p>Promise based HTTP client for the browser and node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/axios/-/axios-0.19.2.tgz">https://registry.npmjs.org/axios/-/axios-0.19.2.tgz</a></p>
<p>Path to dependency file: goscope/frontend/package.json</p>
<p>Path to vulnerable library: goscope/frontend/node_modules/axios/package.json</p>
<p>
Dependency Hierarchy:
- :x: **axios-0.19.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/averageflow/goscope/commit/87e931df1893b08d2613c7fb98649afc3d0536eb">87e931df1893b08d2613c7fb98649afc3d0536eb</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Axios NPM package 0.21.0 contains a Server-Side Request Forgery (SSRF) vulnerability where an attacker is able to bypass a proxy by providing a URL that responds with a redirect to a restricted host or IP address.
<p>Publish Date: 2020-11-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28168>CVE-2020-28168</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-28168 (Medium) detected in axios-0.19.2.tgz - ## CVE-2020-28168 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>axios-0.19.2.tgz</b></p></summary>
<p>Promise based HTTP client for the browser and node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/axios/-/axios-0.19.2.tgz">https://registry.npmjs.org/axios/-/axios-0.19.2.tgz</a></p>
<p>Path to dependency file: goscope/frontend/package.json</p>
<p>Path to vulnerable library: goscope/frontend/node_modules/axios/package.json</p>
<p>
Dependency Hierarchy:
- :x: **axios-0.19.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/averageflow/goscope/commit/87e931df1893b08d2613c7fb98649afc3d0536eb">87e931df1893b08d2613c7fb98649afc3d0536eb</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Axios NPM package 0.21.0 contains a Server-Side Request Forgery (SSRF) vulnerability where an attacker is able to bypass a proxy by providing a URL that responds with a redirect to a restricted host or IP address.
<p>Publish Date: 2020-11-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28168>CVE-2020-28168</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in axios tgz cve medium severity vulnerability vulnerable library axios tgz promise based http client for the browser and node js library home page a href path to dependency file goscope frontend package json path to vulnerable library goscope frontend node modules axios package json dependency hierarchy x axios tgz vulnerable library found in head commit a href found in base branch master vulnerability details axios npm package contains a server side request forgery ssrf vulnerability where an attacker is able to bypass a proxy by providing a url that responds with a redirect to a restricted host or ip address publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href step up your open source security game with whitesource | 0 |
290,428 | 32,078,352,086 | IssuesEvent | 2023-09-25 12:30:31 | hinoshiba/news | https://api.github.com/repos/hinoshiba/news | opened | [SecurityWeek] City of Dallas Details Ransomware Attack Impact, Costs | SecurityWeek |
City of Dallas has approved an $8.5 million budget to restore systems following a Royal ransomware attack in May 2023.
The post [City of Dallas Details Ransomware Attack Impact, Costs](https://www.securityweek.com/city-of-dallas-details-ransomware-attack-impact-costs/) appeared first on [SecurityWeek](https://www.securityweek.com).
<https://www.securityweek.com/city-of-dallas-details-ransomware-attack-impact-costs/>
| True | [SecurityWeek] City of Dallas Details Ransomware Attack Impact, Costs -
City of Dallas has approved an $8.5 million budget to restore systems following a Royal ransomware attack in May 2023.
The post [City of Dallas Details Ransomware Attack Impact, Costs](https://www.securityweek.com/city-of-dallas-details-ransomware-attack-impact-costs/) appeared first on [SecurityWeek](https://www.securityweek.com).
<https://www.securityweek.com/city-of-dallas-details-ransomware-attack-impact-costs/>
| non_priority | city of dallas details ransomware attack impact costs city of dallas has approved an million budget to restore systems following a royal ransomware attack in may the post appeared first on | 0 |
81,681 | 31,275,914,773 | IssuesEvent | 2023-08-22 06:14:42 | jOOQ/jOOQ | https://api.github.com/repos/jOOQ/jOOQ | closed | Issue parsing schema with a DEFAULT field. | T: Defect C: Functionality P: Medium E: All Editions | ### Expected behavior
We have a use case where we added a new `Non Null` field to a table and therefore had to specify a `default` value.
We end up with the following in our table `updated_date datetime NOT NULL DEFAULT '1970-01-01 00:00:00',` and jOOQ seems to choke on this:
```
2023-07-17T19:39:52,634+0000 lvl='INFO', log='Metadata', th='Thread-8', xff='', rId='', tok='', aRId='', tRId='', Started priming caches...
2023-07-17T19:39:53,550+0000 lvl='INFO', log='MetaImpl', th='Thread-8', xff='', rId='', tok='', aRId='', tRId='', Cannot parse default expression: 1970-01-01 00:00:00
2023-07-17T19:39:53.551213716Z org.jooq.impl.ParserException: Unexpected content after end of field input: [1:12] 1970-01-01 [*]00:00:00
2023-07-17T19:39:53.551217132Z at org.jooq.impl.DefaultParseContext.exception(ParserImpl.java:13544)
2023-07-17T19:39:53.551219216Z at org.jooq.impl.DefaultParseContext.done(ParserImpl.java:13704)
2023-07-17T19:39:53.551220924Z at org.jooq.impl.DefaultParseContext.parseField0(ParserImpl.java:563)
2023-07-17T19:39:53.551222632Z at org.jooq.impl.ParserImpl.parseField(ParserImpl.java:428)
2023-07-17T19:39:53.551224174Z at org.jooq.impl.ParserImpl.parseField(ParserImpl.java:423)
2023-07-17T19:39:53.551225882Z at org.jooq.impl.MetaImpl$MetaTable.initColumns(MetaImpl.java:1084)
2023-07-17T19:39:53.551227591Z at org.jooq.impl.MetaImpl$MetaTable.<init>(MetaImpl.java:679)
2023-07-17T19:39:53.551229382Z at org.jooq.impl.MetaImpl$MetaSchema.lambda$getTables$2(MetaImpl.java:425)
2023-07-17T19:39:53.551231674Z at org.jooq.impl.Tools.map(Tools.java:2020)
2023-07-17T19:39:53.551233341Z at org.jooq.impl.MetaImpl$MetaSchema.getTables(MetaImpl.java:397)
```
### Actual behavior
Expect the schema to be parsed correctly as it looks like value DDL.
### Steps to reproduce the problem
For more context, see original bug report in our [repo](https://github.com/killbill/killbill/issues/1900)
### jOOQ Version
3.15.12
### Database product and version
Mysql 8.0.33_3
### Java Version
openjdk 11
### OS Version
linux, macos
### JDBC driver name and version (include name if unofficial driver)
mysql-connector-java:8:0:30 | 1.0 | Issue parsing schema with a DEFAULT field. - ### Expected behavior
We have a use case where we added a new `Non Null` field to a table and therefore had to specify a `default` value.
We end up with the following in our table `updated_date datetime NOT NULL DEFAULT '1970-01-01 00:00:00',` and jOOQ seems to choke on this:
```
2023-07-17T19:39:52,634+0000 lvl='INFO', log='Metadata', th='Thread-8', xff='', rId='', tok='', aRId='', tRId='', Started priming caches...
2023-07-17T19:39:53,550+0000 lvl='INFO', log='MetaImpl', th='Thread-8', xff='', rId='', tok='', aRId='', tRId='', Cannot parse default expression: 1970-01-01 00:00:00
2023-07-17T19:39:53.551213716Z org.jooq.impl.ParserException: Unexpected content after end of field input: [1:12] 1970-01-01 [*]00:00:00
2023-07-17T19:39:53.551217132Z at org.jooq.impl.DefaultParseContext.exception(ParserImpl.java:13544)
2023-07-17T19:39:53.551219216Z at org.jooq.impl.DefaultParseContext.done(ParserImpl.java:13704)
2023-07-17T19:39:53.551220924Z at org.jooq.impl.DefaultParseContext.parseField0(ParserImpl.java:563)
2023-07-17T19:39:53.551222632Z at org.jooq.impl.ParserImpl.parseField(ParserImpl.java:428)
2023-07-17T19:39:53.551224174Z at org.jooq.impl.ParserImpl.parseField(ParserImpl.java:423)
2023-07-17T19:39:53.551225882Z at org.jooq.impl.MetaImpl$MetaTable.initColumns(MetaImpl.java:1084)
2023-07-17T19:39:53.551227591Z at org.jooq.impl.MetaImpl$MetaTable.<init>(MetaImpl.java:679)
2023-07-17T19:39:53.551229382Z at org.jooq.impl.MetaImpl$MetaSchema.lambda$getTables$2(MetaImpl.java:425)
2023-07-17T19:39:53.551231674Z at org.jooq.impl.Tools.map(Tools.java:2020)
2023-07-17T19:39:53.551233341Z at org.jooq.impl.MetaImpl$MetaSchema.getTables(MetaImpl.java:397)
```
### Actual behavior
Expect the schema to be parsed correctly as it looks like value DDL.
### Steps to reproduce the problem
For more context, see original bug report in our [repo](https://github.com/killbill/killbill/issues/1900)
### jOOQ Version
3.15.12
### Database product and version
Mysql 8.0.33_3
### Java Version
openjdk 11
### OS Version
linux, macos
### JDBC driver name and version (include name if unofficial driver)
mysql-connector-java:8:0:30 | non_priority | issue parsing schema with a default field expected behavior we have a use case where we added a new non null field to a table and therefore had to specify a default value we end up with the following in our table updated date datetime not null default and jooq seems to choke on this lvl info log metadata th thread xff rid tok arid trid started priming caches lvl info log metaimpl th thread xff rid tok arid trid cannot parse default expression org jooq impl parserexception unexpected content after end of field input at org jooq impl defaultparsecontext exception parserimpl java at org jooq impl defaultparsecontext done parserimpl java at org jooq impl defaultparsecontext parserimpl java at org jooq impl parserimpl parsefield parserimpl java at org jooq impl parserimpl parsefield parserimpl java at org jooq impl metaimpl metatable initcolumns metaimpl java at org jooq impl metaimpl metatable metaimpl java at org jooq impl metaimpl metaschema lambda gettables metaimpl java at org jooq impl tools map tools java at org jooq impl metaimpl metaschema gettables metaimpl java actual behavior expect the schema to be parsed correctly as it looks like value ddl steps to reproduce the problem for more context see original bug report in our jooq version database product and version mysql java version openjdk os version linux macos jdbc driver name and version include name if unofficial driver mysql connector java | 0 |
199,996 | 22,739,373,089 | IssuesEvent | 2022-07-07 01:06:39 | dmartinez777/BinaryToDecimal | https://api.github.com/repos/dmartinez777/BinaryToDecimal | closed | CVE-2020-36049 (High) detected in socket.io-parser-3.3.0.tgz - autoclosed | security vulnerability | ## CVE-2020-36049 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>socket.io-parser-3.3.0.tgz</b></p></summary>
<p>socket.io protocol parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/socket.io-parser/-/socket.io-parser-3.3.0.tgz">https://registry.npmjs.org/socket.io-parser/-/socket.io-parser-3.3.0.tgz</a></p>
<p>Path to dependency file: BinaryToDecimal/package.json</p>
<p>Path to vulnerable library: BinaryToDecimal/node_modules/socket.io-client/node_modules/socket.io-parser/package.json</p>
<p>
Dependency Hierarchy:
- karma-5.1.1.tgz (Root Library)
- socket.io-2.3.0.tgz
- socket.io-client-2.3.0.tgz
- :x: **socket.io-parser-3.3.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dmartinez777/BinaryToDecimal/commit/1035de8fe2bd2064cfa7d25feecf5c61f0fd898f">1035de8fe2bd2064cfa7d25feecf5c61f0fd898f</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
socket.io-parser before 3.4.1 allows attackers to cause a denial of service (memory consumption) via a large packet because a concatenation approach is used.
<p>Publish Date: 2021-01-08
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36049>CVE-2020-36049</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-36049">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-36049</a></p>
<p>Release Date: 2021-01-08</p>
<p>Fix Resolution: socket.io-parser - 3.4.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-36049 (High) detected in socket.io-parser-3.3.0.tgz - autoclosed - ## CVE-2020-36049 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>socket.io-parser-3.3.0.tgz</b></p></summary>
<p>socket.io protocol parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/socket.io-parser/-/socket.io-parser-3.3.0.tgz">https://registry.npmjs.org/socket.io-parser/-/socket.io-parser-3.3.0.tgz</a></p>
<p>Path to dependency file: BinaryToDecimal/package.json</p>
<p>Path to vulnerable library: BinaryToDecimal/node_modules/socket.io-client/node_modules/socket.io-parser/package.json</p>
<p>
Dependency Hierarchy:
- karma-5.1.1.tgz (Root Library)
- socket.io-2.3.0.tgz
- socket.io-client-2.3.0.tgz
- :x: **socket.io-parser-3.3.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dmartinez777/BinaryToDecimal/commit/1035de8fe2bd2064cfa7d25feecf5c61f0fd898f">1035de8fe2bd2064cfa7d25feecf5c61f0fd898f</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
socket.io-parser before 3.4.1 allows attackers to cause a denial of service (memory consumption) via a large packet because a concatenation approach is used.
<p>Publish Date: 2021-01-08
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36049>CVE-2020-36049</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-36049">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-36049</a></p>
<p>Release Date: 2021-01-08</p>
<p>Fix Resolution: socket.io-parser - 3.4.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in socket io parser tgz autoclosed cve high severity vulnerability vulnerable library socket io parser tgz socket io protocol parser library home page a href path to dependency file binarytodecimal package json path to vulnerable library binarytodecimal node modules socket io client node modules socket io parser package json dependency hierarchy karma tgz root library socket io tgz socket io client tgz x socket io parser tgz vulnerable library found in head commit a href found in base branch master vulnerability details socket io parser before allows attackers to cause a denial of service memory consumption via a large packet because a concatenation approach is used publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution socket io parser step up your open source security game with whitesource | 0 |
180,265 | 30,476,261,560 | IssuesEvent | 2023-07-17 16:44:10 | 18F/TLC-crew | https://api.github.com/repos/18F/TLC-crew | opened | Write a case study/post about building customer panels with CISA | design Bet 2 | ### A description of the work
Write a post/study about how 18F worked with CISA to create a customer feedback program which doubled as a recruiting source for their ongoing CX work.
The audience is people new to 18F, government, or unfamiliar with research. Questions to answer or points to make could be:
- Benefits of a customer panel
- How we added a feedback loop to the current CISA/.gov registration process
- Details of the process and steps
- How the panel helped us recruit and gather feedback for the new .gov
### Point of contact on this issue
@alexbielen, @MelissaBraxton @boonerang
**Billable?**
- [ ] Yes
- [X] No
If yes, tock code:
**Skills needed**
- [ ] Any human
- [X] Design
- [ ] Content
- [ ] Engineering
- [ ] Acquisition
- [ ] Product
- [ ] Other
**Timeline**
Does this need to happen in the next two weeks?
- [ ] Yes
- [X] No
How much time do you anticipate this work taking?
Roughly two weeks (depending on editorial review and revisions)
### Acceptance Criteria
- [ ] We have a blog post that explains how 18F worked with CISA, recruited research participants, and how others may use the same methods in their work.
| 1.0 | Write a case study/post about building customer panels with CISA - ### A description of the work
Write a post/study about how 18F worked with CISA to create a customer feedback program which doubled as a recruiting source for their ongoing CX work.
The audience is people new to 18F, government, or unfamiliar with research. Questions to answer or points to make could be:
- Benefits of a customer panel
- How we added a feedback loop to the current CISA/.gov registration process
- Details of the process and steps
- How the panel helped us recruit and gather feedback for the new .gov
### Point of contact on this issue
@alexbielen, @MelissaBraxton @boonerang
**Billable?**
- [ ] Yes
- [X] No
If yes, tock code:
**Skills needed**
- [ ] Any human
- [X] Design
- [ ] Content
- [ ] Engineering
- [ ] Acquisition
- [ ] Product
- [ ] Other
**Timeline**
Does this need to happen in the next two weeks?
- [ ] Yes
- [X] No
How much time do you anticipate this work taking?
Roughly two weeks (depending on editorial review and revisions)
### Acceptance Criteria
- [ ] We have a blog post that explains how 18F worked with CISA, recruited research participants, and how others may use the same methods in their work.
| non_priority | write a case study post about building customer panels with cisa a description of the work write a post study about how worked with cisa to create a customer feedback program which doubled as a recruiting source for their ongoing cx work the audience is people new to government or unfamiliar with research questions to answer or points to make could be benefits of a customer panel how we added a feedback loop to the current cisa gov registration process details of the process and steps how the panel helped us recruit and gather feedback for the new gov point of contact on this issue alexbielen melissabraxton boonerang billable yes no if yes tock code skills needed any human design content engineering acquisition product other timeline does this need to happen in the next two weeks yes no how much time do you anticipate this work taking roughly two weeks depending on editorial review and revisions acceptance criteria we have a blog post that explains how worked with cisa recruited research participants and how others may use the same methods in their work | 0 |
82,903 | 16,060,119,227 | IssuesEvent | 2021-04-23 11:18:17 | towavephone/GatsbyBlog | https://api.github.com/repos/towavephone/GatsbyBlog | opened | 微前端框架qiankun源码笔记 | /qiankun-code-note/ Gitalk | /qiankun-code-note/定义 是一种类似于微服务的架构,它将微服务的理念应用于浏览器端,即将单页面前端应用由单一的单体应用转变为多个小型前端应用聚合为一的应用。各个前端应用还可以独立开发、独立部署。同时,它们也可以在共享组件的同时进行并行开发——这些组件可以通过 NPM 或者 Git Tag、Git… | 1.0 | 微前端框架qiankun源码笔记 - /qiankun-code-note/定义 是一种类似于微服务的架构,它将微服务的理念应用于浏览器端,即将单页面前端应用由单一的单体应用转变为多个小型前端应用聚合为一的应用。各个前端应用还可以独立开发、独立部署。同时,它们也可以在共享组件的同时进行并行开发——这些组件可以通过 NPM 或者 Git Tag、Git… | non_priority | 微前端框架qiankun源码笔记 qiankun code note 定义 是一种类似于微服务的架构,它将微服务的理念应用于浏览器端,即将单页面前端应用由单一的单体应用转变为多个小型前端应用聚合为一的应用。各个前端应用还可以独立开发、独立部署。同时,它们也可以在共享组件的同时进行并行开发——这些组件可以通过 npm 或者 git tag、git… | 0 |
19,293 | 10,340,708,755 | IssuesEvent | 2019-09-03 22:57:31 | mikaelkrief/Learning_DevOps | https://api.github.com/repos/mikaelkrief/Learning_DevOps | opened | WS-2018-0236 (Medium) detected in mem-1.1.0.tgz | security vulnerability | ## WS-2018-0236 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mem-1.1.0.tgz</b></p></summary>
<p>Memoize functions - An optimization used to speed up consecutive function calls by caching the result of calls with identical input</p>
<p>Library home page: <a href="https://registry.npmjs.org/mem/-/mem-1.1.0.tgz">https://registry.npmjs.org/mem/-/mem-1.1.0.tgz</a></p>
<p>Path to dependency file: /Learning_DevOps/CHAP10/AppDemo/package.json</p>
<p>Path to vulnerable library: /tmp/git/Learning_DevOps/CHAP10/AppDemo/node_modules/mem/package.json</p>
<p>
Dependency Hierarchy:
- jest-23.6.0.tgz (Root Library)
- jest-cli-23.6.0.tgz
- yargs-11.1.0.tgz
- os-locale-2.1.0.tgz
- :x: **mem-1.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/mikaelkrief/Learning_DevOps/commit/64bf284ae4358b2a0bb8e5d7cf619e0050cb8ab0">64bf284ae4358b2a0bb8e5d7cf619e0050cb8ab0</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In nodejs-mem before version 4.0.0 there is a memory leak due to old results not being removed from the cache despite reaching maxAge. Exploitation of this can lead to exhaustion of memory and subsequent denial of service.
<p>Publish Date: 2019-05-30
<p>URL: <a href=https://bugzilla.redhat.com/show_bug.cgi?id=1623744>WS-2018-0236</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1623744">https://bugzilla.redhat.com/show_bug.cgi?id=1623744</a></p>
<p>Release Date: 2019-05-30</p>
<p>Fix Resolution: 4.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2018-0236 (Medium) detected in mem-1.1.0.tgz - ## WS-2018-0236 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mem-1.1.0.tgz</b></p></summary>
<p>Memoize functions - An optimization used to speed up consecutive function calls by caching the result of calls with identical input</p>
<p>Library home page: <a href="https://registry.npmjs.org/mem/-/mem-1.1.0.tgz">https://registry.npmjs.org/mem/-/mem-1.1.0.tgz</a></p>
<p>Path to dependency file: /Learning_DevOps/CHAP10/AppDemo/package.json</p>
<p>Path to vulnerable library: /tmp/git/Learning_DevOps/CHAP10/AppDemo/node_modules/mem/package.json</p>
<p>
Dependency Hierarchy:
- jest-23.6.0.tgz (Root Library)
- jest-cli-23.6.0.tgz
- yargs-11.1.0.tgz
- os-locale-2.1.0.tgz
- :x: **mem-1.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/mikaelkrief/Learning_DevOps/commit/64bf284ae4358b2a0bb8e5d7cf619e0050cb8ab0">64bf284ae4358b2a0bb8e5d7cf619e0050cb8ab0</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In nodejs-mem before version 4.0.0 there is a memory leak due to old results not being removed from the cache despite reaching maxAge. Exploitation of this can lead to exhaustion of memory and subsequent denial of service.
<p>Publish Date: 2019-05-30
<p>URL: <a href=https://bugzilla.redhat.com/show_bug.cgi?id=1623744>WS-2018-0236</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1623744">https://bugzilla.redhat.com/show_bug.cgi?id=1623744</a></p>
<p>Release Date: 2019-05-30</p>
<p>Fix Resolution: 4.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in mem tgz ws medium severity vulnerability vulnerable library mem tgz memoize functions an optimization used to speed up consecutive function calls by caching the result of calls with identical input library home page a href path to dependency file learning devops appdemo package json path to vulnerable library tmp git learning devops appdemo node modules mem package json dependency hierarchy jest tgz root library jest cli tgz yargs tgz os locale tgz x mem tgz vulnerable library found in head commit a href vulnerability details in nodejs mem before version there is a memory leak due to old results not being removed from the cache despite reaching maxage exploitation of this can lead to exhaustion of memory and subsequent denial of service publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
273,382 | 20,790,122,279 | IssuesEvent | 2022-03-17 00:27:11 | ComteHerrapait/adp_but_better | https://api.github.com/repos/ComteHerrapait/adp_but_better | closed | add unit tests | documentation enhancement | - [x] create unit tests
- [ ] implement unit tests to pre-commit hook
- [x] automate unit tests in github actions | 1.0 | add unit tests - - [x] create unit tests
- [ ] implement unit tests to pre-commit hook
- [x] automate unit tests in github actions | non_priority | add unit tests create unit tests implement unit tests to pre commit hook automate unit tests in github actions | 0 |
36,630 | 8,037,357,201 | IssuesEvent | 2018-07-30 12:22:59 | OpenMS/OpenMS | https://api.github.com/repos/OpenMS/OpenMS | closed | FFMultiplex broken | blocker defect | I get some weird results in label-free analysis. Maybe related to the refactoring into a class.
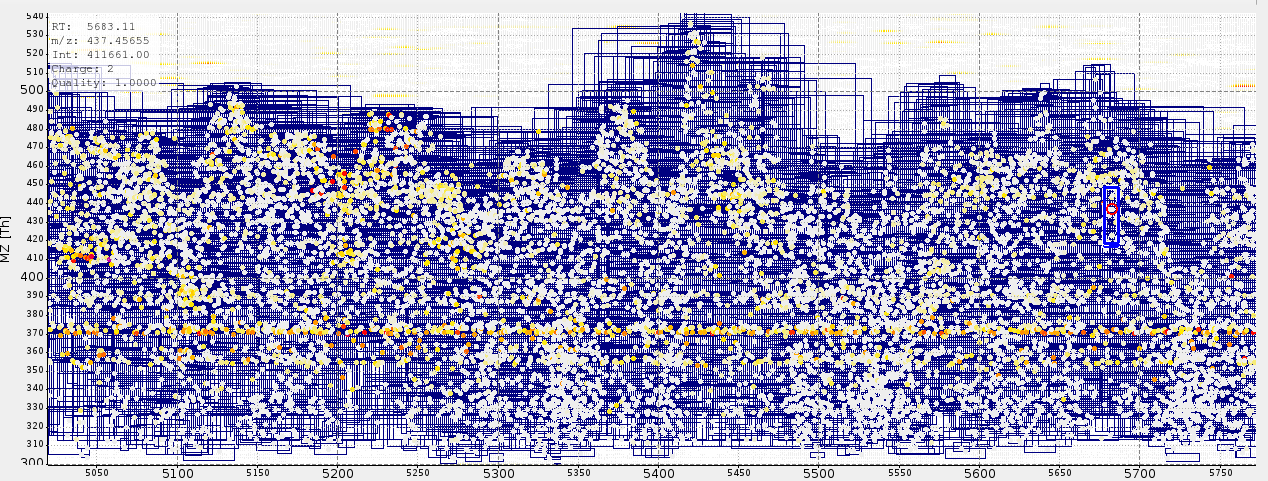
| 1.0 | FFMultiplex broken - I get some weird results in label-free analysis. Maybe related to the refactoring into a class.
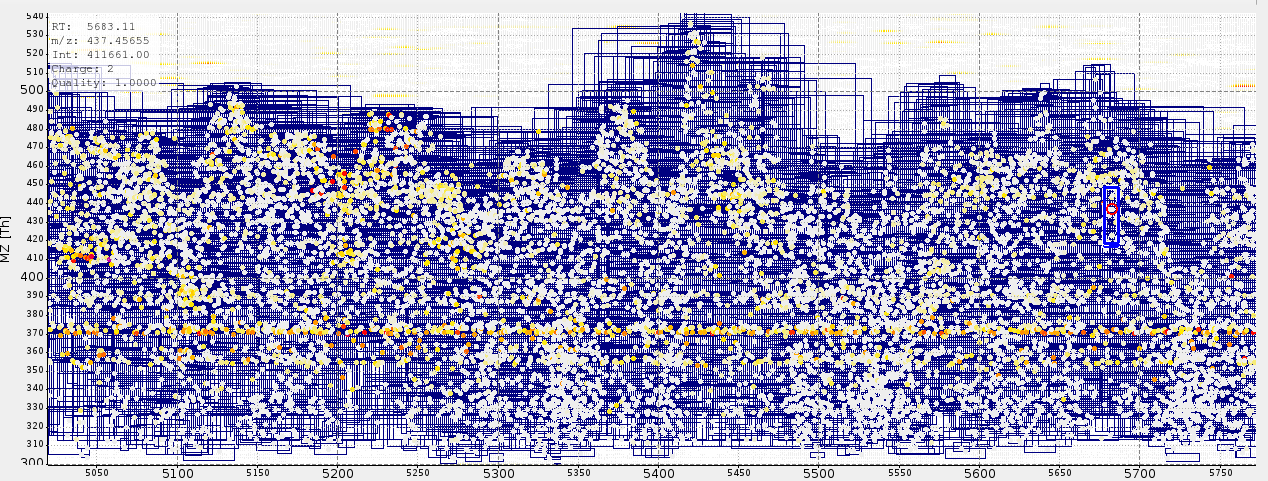
| non_priority | ffmultiplex broken i get some weird results in label free analysis maybe related to the refactoring into a class | 0 |
318,048 | 23,701,548,913 | IssuesEvent | 2022-08-29 19:30:37 | celestiaorg/celestia-specs | https://api.github.com/repos/celestiaorg/celestia-specs | opened | Migrate specs to individual repos | documentation investigation | ## Context
- https://github.com/celestiaorg/celestia-app/issues/650
## Candidates Repos
It may aid discoverability if these specs are migrated to a consistent location across repos (i.e. `specs/`)
- https://github.com/celestiaorg/celestia-core
- https://github.com/celestiaorg/celestia-app
- https://github.com/celestiaorg/celestia-node
- https://github.com/celestiaorg/docs
- https://github.com/celestiaorg/celestia.org
## Cursory Breakdown
Page | Repo | Notes
--- | --- | ---
`architecture.md` | docs or celestia.org |
`block_proposer.md` | celestia-app
`consensus.md` | celestia-core
`data_structures.md` | celestia-app and celestia-core
`light_client.md` | | empty so removable
`networking.md` | celestia-app and celestia-core
`node_types.md` | celestia-node
`specification.md` | | table of contents so removable
`distributing_rewards.md` | celestia-core
`fork_choice_das.md` | docs or celestia.org |
`message_block_layout.md` | celestia-app
`rational.md` | | table of contents so removable
`rewards.md` | celestia-core
| 1.0 | Migrate specs to individual repos - ## Context
- https://github.com/celestiaorg/celestia-app/issues/650
## Candidates Repos
It may aid discoverability if these specs are migrated to a consistent location across repos (i.e. `specs/`)
- https://github.com/celestiaorg/celestia-core
- https://github.com/celestiaorg/celestia-app
- https://github.com/celestiaorg/celestia-node
- https://github.com/celestiaorg/docs
- https://github.com/celestiaorg/celestia.org
## Cursory Breakdown
Page | Repo | Notes
--- | --- | ---
`architecture.md` | docs or celestia.org |
`block_proposer.md` | celestia-app
`consensus.md` | celestia-core
`data_structures.md` | celestia-app and celestia-core
`light_client.md` | | empty so removable
`networking.md` | celestia-app and celestia-core
`node_types.md` | celestia-node
`specification.md` | | table of contents so removable
`distributing_rewards.md` | celestia-core
`fork_choice_das.md` | docs or celestia.org |
`message_block_layout.md` | celestia-app
`rational.md` | | table of contents so removable
`rewards.md` | celestia-core
| non_priority | migrate specs to individual repos context candidates repos it may aid discoverability if these specs are migrated to a consistent location across repos i e specs cursory breakdown page repo notes architecture md docs or celestia org block proposer md celestia app consensus md celestia core data structures md celestia app and celestia core light client md empty so removable networking md celestia app and celestia core node types md celestia node specification md table of contents so removable distributing rewards md celestia core fork choice das md docs or celestia org message block layout md celestia app rational md table of contents so removable rewards md celestia core | 0 |
8,755 | 4,318,903,018 | IssuesEvent | 2016-07-24 10:11:53 | opencv/opencv | https://api.github.com/repos/opencv/opencv | closed | issue with building from source | bug category: build/install | <!--
If you have a question rather than reporting a bug please go to http://answers.opencv.org where you get much faster responses.
If you need further assistance please read [How To Contribute](https://github.com/opencv/opencv/wiki/How_to_contribute).
This is a template helping you to create an issue which can be processed as quickly as possible. This is the bug reporting section for the OpenCV library.
-->
##### System information (version)
<!-- Example
- OpenCV => 3.1
- Operating System / Platform => Windows 64 Bit
- Compiler => Visual Studio 2015
-->
- OpenCV => master
- Operating System / Platform => ubuntu 16.04
- Compiler => g++/cmake
##### Detailed description
<!-- your description -->
make command showing error after successful completion of cmake while building from source.
following this-> https://github.com/BVLC/caffe/wiki/Ubuntu-16.04-or-15.10-OpenCV-3.1-Installation-Guide

##### Steps to reproduce
<!-- to add code example fence it with triple backticks and optional file extension
```.cpp
// C++ code example
```
or attach as .txt or .zip file
--> | 1.0 | issue with building from source - <!--
If you have a question rather than reporting a bug please go to http://answers.opencv.org where you get much faster responses.
If you need further assistance please read [How To Contribute](https://github.com/opencv/opencv/wiki/How_to_contribute).
This is a template helping you to create an issue which can be processed as quickly as possible. This is the bug reporting section for the OpenCV library.
-->
##### System information (version)
<!-- Example
- OpenCV => 3.1
- Operating System / Platform => Windows 64 Bit
- Compiler => Visual Studio 2015
-->
- OpenCV => master
- Operating System / Platform => ubuntu 16.04
- Compiler => g++/cmake
##### Detailed description
<!-- your description -->
make command showing error after successful completion of cmake while building from source.
following this-> https://github.com/BVLC/caffe/wiki/Ubuntu-16.04-or-15.10-OpenCV-3.1-Installation-Guide

##### Steps to reproduce
<!-- to add code example fence it with triple backticks and optional file extension
```.cpp
// C++ code example
```
or attach as .txt or .zip file
--> | non_priority | issue with building from source if you have a question rather than reporting a bug please go to where you get much faster responses if you need further assistance please read this is a template helping you to create an issue which can be processed as quickly as possible this is the bug reporting section for the opencv library system information version example opencv operating system platform windows bit compiler visual studio opencv master operating system platform ubuntu compiler g cmake detailed description make command showing error after successful completion of cmake while building from source following this steps to reproduce to add code example fence it with triple backticks and optional file extension cpp c code example or attach as txt or zip file | 0 |
159,150 | 20,036,655,921 | IssuesEvent | 2022-02-02 12:38:56 | kapseliboi/webuild | https://api.github.com/repos/kapseliboi/webuild | opened | CVE-2021-37713 (High) detected in tar-4.4.4.tgz | security vulnerability | ## CVE-2021-37713 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-4.4.4.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-4.4.4.tgz">https://registry.npmjs.org/tar/-/tar-4.4.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grpc/node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-5.13.0.tgz (Root Library)
- firestore-0.15.4.tgz
- google-gax-0.17.1.tgz
- grpc-1.13.0.tgz
- node-pre-gyp-0.10.2.tgz
- :x: **tar-4.4.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/webuild/commit/cfe337e0888ede79847ee4201c96d43ab06dc89e">cfe337e0888ede79847ee4201c96d43ab06dc89e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The npm package "tar" (aka node-tar) before versions 4.4.18, 5.0.10, and 6.1.9 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be outside of the extraction target directory is not extracted. This is, in part, accomplished by sanitizing absolute paths of entries within the archive, skipping archive entries that contain `..` path portions, and resolving the sanitized paths against the extraction target directory. This logic was insufficient on Windows systems when extracting tar files that contained a path that was not an absolute path, but specified a drive letter different from the extraction target, such as `C:some\path`. If the drive letter does not match the extraction target, for example `D:\extraction\dir`, then the result of `path.resolve(extractionDirectory, entryPath)` would resolve against the current working directory on the `C:` drive, rather than the extraction target directory. Additionally, a `..` portion of the path could occur immediately after the drive letter, such as `C:../foo`, and was not properly sanitized by the logic that checked for `..` within the normalized and split portions of the path. This only affects users of `node-tar` on Windows systems. These issues were addressed in releases 4.4.18, 5.0.10 and 6.1.9. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. There is no reasonable way to work around this issue without performing the same path normalization procedures that node-tar now does. Users are encouraged to upgrade to the latest patched versions of node-tar, rather than attempt to sanitize paths themselves.
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37713>CVE-2021-37713</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-5955-9wpr-37jh">https://github.com/npm/node-tar/security/advisories/GHSA-5955-9wpr-37jh</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution (tar): 4.4.18</p>
<p>Direct dependency fix Resolution (firebase-admin): 5.13.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-37713 (High) detected in tar-4.4.4.tgz - ## CVE-2021-37713 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-4.4.4.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-4.4.4.tgz">https://registry.npmjs.org/tar/-/tar-4.4.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grpc/node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-5.13.0.tgz (Root Library)
- firestore-0.15.4.tgz
- google-gax-0.17.1.tgz
- grpc-1.13.0.tgz
- node-pre-gyp-0.10.2.tgz
- :x: **tar-4.4.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/webuild/commit/cfe337e0888ede79847ee4201c96d43ab06dc89e">cfe337e0888ede79847ee4201c96d43ab06dc89e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The npm package "tar" (aka node-tar) before versions 4.4.18, 5.0.10, and 6.1.9 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be outside of the extraction target directory is not extracted. This is, in part, accomplished by sanitizing absolute paths of entries within the archive, skipping archive entries that contain `..` path portions, and resolving the sanitized paths against the extraction target directory. This logic was insufficient on Windows systems when extracting tar files that contained a path that was not an absolute path, but specified a drive letter different from the extraction target, such as `C:some\path`. If the drive letter does not match the extraction target, for example `D:\extraction\dir`, then the result of `path.resolve(extractionDirectory, entryPath)` would resolve against the current working directory on the `C:` drive, rather than the extraction target directory. Additionally, a `..` portion of the path could occur immediately after the drive letter, such as `C:../foo`, and was not properly sanitized by the logic that checked for `..` within the normalized and split portions of the path. This only affects users of `node-tar` on Windows systems. These issues were addressed in releases 4.4.18, 5.0.10 and 6.1.9. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. There is no reasonable way to work around this issue without performing the same path normalization procedures that node-tar now does. Users are encouraged to upgrade to the latest patched versions of node-tar, rather than attempt to sanitize paths themselves.
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37713>CVE-2021-37713</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-5955-9wpr-37jh">https://github.com/npm/node-tar/security/advisories/GHSA-5955-9wpr-37jh</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution (tar): 4.4.18</p>
<p>Direct dependency fix Resolution (firebase-admin): 5.13.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in tar tgz cve high severity vulnerability vulnerable library tar tgz tar for node library home page a href path to dependency file package json path to vulnerable library node modules grpc node modules tar package json dependency hierarchy firebase admin tgz root library firestore tgz google gax tgz grpc tgz node pre gyp tgz x tar tgz vulnerable library found in head commit a href found in base branch master vulnerability details the npm package tar aka node tar before versions and has an arbitrary file creation overwrite and arbitrary code execution vulnerability node tar aims to guarantee that any file whose location would be outside of the extraction target directory is not extracted this is in part accomplished by sanitizing absolute paths of entries within the archive skipping archive entries that contain path portions and resolving the sanitized paths against the extraction target directory this logic was insufficient on windows systems when extracting tar files that contained a path that was not an absolute path but specified a drive letter different from the extraction target such as c some path if the drive letter does not match the extraction target for example d extraction dir then the result of path resolve extractiondirectory entrypath would resolve against the current working directory on the c drive rather than the extraction target directory additionally a portion of the path could occur immediately after the drive letter such as c foo and was not properly sanitized by the logic that checked for within the normalized and split portions of the path this only affects users of node tar on windows systems these issues were addressed in releases and the branch of node tar has been deprecated and did not receive patches for these issues if you are still using a release we recommend you update to a more recent version of node tar there is no reasonable way to work around this issue without performing the same path normalization procedures that node tar now does users are encouraged to upgrade to the latest patched versions of node tar rather than attempt to sanitize paths themselves publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tar direct dependency fix resolution firebase admin step up your open source security game with whitesource | 0 |
99,044 | 20,842,078,747 | IssuesEvent | 2022-03-21 02:13:42 | CleverRaven/Cataclysm-DDA | https://api.github.com/repos/CleverRaven/Cataclysm-DDA | closed | Debug spawning item menu "find" no longer working again | (S1 - Need confirmation) Code: Debug | ### Describe the bug
Use the ‘find’ function in the debug item spawning menu cannot input any words and also block the [quit] function. It looks similar to the issue #54355
### Steps to reproduce
1.Into the debug spawn menu
2.Press [/] to active find function
3.You will find you cannot type any character or even quit the mune
### Expected behavior
Normally using the filter and quit
### Screenshots
_No response_
### Versions and configuration
- OS: Windows
- OS Version: 10.0.19044.1586 (21H2)
- Game Version: b0a8d8c [64-bit]
- Graphics Version: Tiles
- Game Language: 系统语言 []
- Mods loaded: [
浩劫余生 [dda],
禁用NPC需求 [no_npc_food],
禁止真菌增殖 [no_fungal_growth],
生化职业 [package_bionic_professions]
]
### Additional context
_No response_ | 1.0 | Debug spawning item menu "find" no longer working again - ### Describe the bug
Use the ‘find’ function in the debug item spawning menu cannot input any words and also block the [quit] function. It looks similar to the issue #54355
### Steps to reproduce
1.Into the debug spawn menu
2.Press [/] to active find function
3.You will find you cannot type any character or even quit the mune
### Expected behavior
Normally using the filter and quit
### Screenshots
_No response_
### Versions and configuration
- OS: Windows
- OS Version: 10.0.19044.1586 (21H2)
- Game Version: b0a8d8c [64-bit]
- Graphics Version: Tiles
- Game Language: 系统语言 []
- Mods loaded: [
浩劫余生 [dda],
禁用NPC需求 [no_npc_food],
禁止真菌增殖 [no_fungal_growth],
生化职业 [package_bionic_professions]
]
### Additional context
_No response_ | non_priority | debug spawning item menu find no longer working again describe the bug use the ‘find’ function in the debug item spawning menu cannot input any words and also block the function it looks similar to the issue steps to reproduce into the debug spawn menu press to active find function you will find you cannot type any character or even quit the mune expected behavior normally using the filter and quit screenshots no response versions and configuration os windows os version game version graphics version tiles game language 系统语言 mods loaded 浩劫余生 禁用npc需求 禁止真菌增殖 生化职业 additional context no response | 0 |
3,921 | 6,843,043,013 | IssuesEvent | 2017-11-12 10:48:24 | pwittchen/ReactiveNetwork | https://api.github.com/repos/pwittchen/ReactiveNetwork | opened | RxJava1.x: release 0.12.2 | release process | **Initial realese notes**:
- updated project dependencies
- updated Gradle to 3.0.0
**Things to do**:
- [ ] RxJava1.x branch:
- [ ] bump library version
- [ ] upload archives to Maven Central
- [ ] close and release artifact on Maven Central
- [ ] update `CHANGELOG.md` after Maven Sync
- [ ] bump library version in `README.md`
- [ ] create new GitHub release | 1.0 | RxJava1.x: release 0.12.2 - **Initial realese notes**:
- updated project dependencies
- updated Gradle to 3.0.0
**Things to do**:
- [ ] RxJava1.x branch:
- [ ] bump library version
- [ ] upload archives to Maven Central
- [ ] close and release artifact on Maven Central
- [ ] update `CHANGELOG.md` after Maven Sync
- [ ] bump library version in `README.md`
- [ ] create new GitHub release | non_priority | x release initial realese notes updated project dependencies updated gradle to things to do x branch bump library version upload archives to maven central close and release artifact on maven central update changelog md after maven sync bump library version in readme md create new github release | 0 |
151,517 | 19,654,623,203 | IssuesEvent | 2022-01-10 11:09:07 | theWhiteFox/react-tic-tac-toe | https://api.github.com/repos/theWhiteFox/react-tic-tac-toe | opened | CVE-2019-20149 (High) detected in kind-of-6.0.2.tgz | security vulnerability | ## CVE-2019-20149 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>kind-of-6.0.2.tgz</b></p></summary>
<p>Get the native type of a value.</p>
<p>Library home page: <a href="https://registry.npmjs.org/kind-of/-/kind-of-6.0.2.tgz">https://registry.npmjs.org/kind-of/-/kind-of-6.0.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/kind-of/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.1.tgz (Root Library)
- sass-loader-8.0.2.tgz
- clone-deep-4.0.1.tgz
- :x: **kind-of-6.0.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/theWhiteFox/react-tic-tac-toe/commit/e334886398cc42d1544bbf041c785f1d8e0d5d00">e334886398cc42d1544bbf041c785f1d8e0d5d00</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ctorName in index.js in kind-of v6.0.2 allows external user input to overwrite certain internal attributes via a conflicting name, as demonstrated by 'constructor': {'name':'Symbol'}. Hence, a crafted payload can overwrite this builtin attribute to manipulate the type detection result.
<p>Publish Date: 2019-12-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-20149>CVE-2019-20149</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-20149">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-20149</a></p>
<p>Release Date: 2020-08-24</p>
<p>Fix Resolution: 6.0.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-20149 (High) detected in kind-of-6.0.2.tgz - ## CVE-2019-20149 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>kind-of-6.0.2.tgz</b></p></summary>
<p>Get the native type of a value.</p>
<p>Library home page: <a href="https://registry.npmjs.org/kind-of/-/kind-of-6.0.2.tgz">https://registry.npmjs.org/kind-of/-/kind-of-6.0.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/kind-of/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.1.tgz (Root Library)
- sass-loader-8.0.2.tgz
- clone-deep-4.0.1.tgz
- :x: **kind-of-6.0.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/theWhiteFox/react-tic-tac-toe/commit/e334886398cc42d1544bbf041c785f1d8e0d5d00">e334886398cc42d1544bbf041c785f1d8e0d5d00</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ctorName in index.js in kind-of v6.0.2 allows external user input to overwrite certain internal attributes via a conflicting name, as demonstrated by 'constructor': {'name':'Symbol'}. Hence, a crafted payload can overwrite this builtin attribute to manipulate the type detection result.
<p>Publish Date: 2019-12-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-20149>CVE-2019-20149</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-20149">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-20149</a></p>
<p>Release Date: 2020-08-24</p>
<p>Fix Resolution: 6.0.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in kind of tgz cve high severity vulnerability vulnerable library kind of tgz get the native type of a value library home page a href path to dependency file package json path to vulnerable library node modules kind of package json dependency hierarchy react scripts tgz root library sass loader tgz clone deep tgz x kind of tgz vulnerable library found in head commit a href found in base branch master vulnerability details ctorname in index js in kind of allows external user input to overwrite certain internal attributes via a conflicting name as demonstrated by constructor name symbol hence a crafted payload can overwrite this builtin attribute to manipulate the type detection result publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
5,361 | 3,918,153,205 | IssuesEvent | 2016-04-21 11:15:01 | kolliSuman/issues | https://api.github.com/repos/kolliSuman/issues | closed | QA_Free Vibration of Single Degree of Freedom System_Back to experiments_smk | Category: Usability Developed By: VLEAD Release Number: Production Severity: S2 Status: Open | Defect Description :
In the "Free Vibration of Single Degree of Freedom System" experiment,the back to experiments link is not present in the page instead the back to experiments link should be displayed on the screen in-order to view the list of experiments by the user.
Actual Result :
In the "Free Vibration of Single Degree of Freedom System" experiment,the back to experiments link is not present in the page.
Environment :
OS: Windows 7, Ubuntu-16.04,Centos-6
Browsers: Firefox-42.0,Chrome-47.0,chromium-45.0
Bandwidth : 100Mbps
Hardware Configuration:8GBRAM
Processor:i5
Test Step Link:
https://github.com/Virtual-Labs/Structural Dynami/blob/master/test-cases/integration_test-cases/Free%20Vibration%20of%20Single%20Degree%20of%20Freedom%20System/Free%20Vibration%20of%20Single%20Degree%20of%20Freedom%20System_16_Back%20to%20experiments_smk.org | True | QA_Free Vibration of Single Degree of Freedom System_Back to experiments_smk - Defect Description :
In the "Free Vibration of Single Degree of Freedom System" experiment,the back to experiments link is not present in the page instead the back to experiments link should be displayed on the screen in-order to view the list of experiments by the user.
Actual Result :
In the "Free Vibration of Single Degree of Freedom System" experiment,the back to experiments link is not present in the page.
Environment :
OS: Windows 7, Ubuntu-16.04,Centos-6
Browsers: Firefox-42.0,Chrome-47.0,chromium-45.0
Bandwidth : 100Mbps
Hardware Configuration:8GBRAM
Processor:i5
Test Step Link:
https://github.com/Virtual-Labs/Structural Dynami/blob/master/test-cases/integration_test-cases/Free%20Vibration%20of%20Single%20Degree%20of%20Freedom%20System/Free%20Vibration%20of%20Single%20Degree%20of%20Freedom%20System_16_Back%20to%20experiments_smk.org | non_priority | qa free vibration of single degree of freedom system back to experiments smk defect description in the free vibration of single degree of freedom system experiment the back to experiments link is not present in the page instead the back to experiments link should be displayed on the screen in order to view the list of experiments by the user actual result in the free vibration of single degree of freedom system experiment the back to experiments link is not present in the page environment os windows ubuntu centos browsers firefox chrome chromium bandwidth hardware configuration processor test step link dynami blob master test cases integration test cases free free back smk org | 0 |
278,018 | 30,702,156,161 | IssuesEvent | 2023-07-27 01:07:13 | MidnightBSD/src | https://api.github.com/repos/MidnightBSD/src | opened | CVE-2023-38408 (High) detected in multiple libraries | Mend: dependency security vulnerability | ## CVE-2023-38408 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>openssh-portableV_9_3_P2</b>, <b>openssh-portableV_9_3_P2</b>, <b>openssh-portableV_9_3_P2</b>, <b>openssh-portableV_9_3_P2</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The PKCS#11 feature in ssh-agent in OpenSSH before 9.3p2 has an insufficiently trustworthy search path, leading to remote code execution if an agent is forwarded to an attacker-controlled system. (Code in /usr/lib is not necessarily safe for loading into ssh-agent.) NOTE: this issue exists because of an incomplete fix for CVE-2016-10009.
<p>Publish Date: 2023-07-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-38408>CVE-2023-38408</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://seclists.org/oss-sec/2023/q3/48">https://seclists.org/oss-sec/2023/q3/48</a></p>
<p>Release Date: 2023-07-20</p>
<p>Fix Resolution: V_9_3_P2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2023-38408 (High) detected in multiple libraries - ## CVE-2023-38408 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>openssh-portableV_9_3_P2</b>, <b>openssh-portableV_9_3_P2</b>, <b>openssh-portableV_9_3_P2</b>, <b>openssh-portableV_9_3_P2</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The PKCS#11 feature in ssh-agent in OpenSSH before 9.3p2 has an insufficiently trustworthy search path, leading to remote code execution if an agent is forwarded to an attacker-controlled system. (Code in /usr/lib is not necessarily safe for loading into ssh-agent.) NOTE: this issue exists because of an incomplete fix for CVE-2016-10009.
<p>Publish Date: 2023-07-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-38408>CVE-2023-38408</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://seclists.org/oss-sec/2023/q3/48">https://seclists.org/oss-sec/2023/q3/48</a></p>
<p>Release Date: 2023-07-20</p>
<p>Fix Resolution: V_9_3_P2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries openssh portablev openssh portablev openssh portablev openssh portablev vulnerability details the pkcs feature in ssh agent in openssh before has an insufficiently trustworthy search path leading to remote code execution if an agent is forwarded to an attacker controlled system code in usr lib is not necessarily safe for loading into ssh agent note this issue exists because of an incomplete fix for cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution v step up your open source security game with mend | 0 |
284,178 | 30,913,600,473 | IssuesEvent | 2023-08-05 02:21:39 | panasalap/linux-4.19.72_Fix | https://api.github.com/repos/panasalap/linux-4.19.72_Fix | reopened | CVE-2021-20292 (Medium) detected in linux-yoctov5.4.51 | Mend: dependency security vulnerability | ## CVE-2021-20292 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in HEAD commit: <a href="https://github.com/panasalap/linux-4.19.72/commit/fc232d9ef12e2320ea3e8cb3de916a34aad68b6a">fc232d9ef12e2320ea3e8cb3de916a34aad68b6a</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/gpu/drm/ttm/ttm_tt.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/gpu/drm/ttm/ttm_tt.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
There is a flaw reported in the Linux kernel in versions before 5.9 in drivers/gpu/drm/nouveau/nouveau_sgdma.c in nouveau_sgdma_create_ttm in Nouveau DRM subsystem. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker with a local account with a root privilege, can leverage this vulnerability to escalate privileges and execute code in the context of the kernel.
<p>Publish Date: 2021-05-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-20292>CVE-2021-20292</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2021-20292">https://www.linuxkernelcves.com/cves/CVE-2021-20292</a></p>
<p>Release Date: 2021-05-28</p>
<p>Fix Resolution: v4.19.140, v5.4.59, v5.7.16, v5.8.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-20292 (Medium) detected in linux-yoctov5.4.51 - ## CVE-2021-20292 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in HEAD commit: <a href="https://github.com/panasalap/linux-4.19.72/commit/fc232d9ef12e2320ea3e8cb3de916a34aad68b6a">fc232d9ef12e2320ea3e8cb3de916a34aad68b6a</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/gpu/drm/ttm/ttm_tt.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/gpu/drm/ttm/ttm_tt.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
There is a flaw reported in the Linux kernel in versions before 5.9 in drivers/gpu/drm/nouveau/nouveau_sgdma.c in nouveau_sgdma_create_ttm in Nouveau DRM subsystem. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker with a local account with a root privilege, can leverage this vulnerability to escalate privileges and execute code in the context of the kernel.
<p>Publish Date: 2021-05-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-20292>CVE-2021-20292</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2021-20292">https://www.linuxkernelcves.com/cves/CVE-2021-20292</a></p>
<p>Release Date: 2021-05-28</p>
<p>Fix Resolution: v4.19.140, v5.4.59, v5.7.16, v5.8.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linux cve medium severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in head commit a href found in base branch master vulnerable source files drivers gpu drm ttm ttm tt c drivers gpu drm ttm ttm tt c vulnerability details there is a flaw reported in the linux kernel in versions before in drivers gpu drm nouveau nouveau sgdma c in nouveau sgdma create ttm in nouveau drm subsystem the issue results from the lack of validating the existence of an object prior to performing operations on the object an attacker with a local account with a root privilege can leverage this vulnerability to escalate privileges and execute code in the context of the kernel publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
139,843 | 18,858,054,452 | IssuesEvent | 2021-11-12 09:20:02 | Verseghy/website_frontend | https://api.github.com/repos/Verseghy/website_frontend | closed | CVE-2021-33587 (High) detected in css-what-4.0.0.tgz | security vulnerability | ## CVE-2021-33587 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>css-what-4.0.0.tgz</b></p></summary>
<p>a CSS selector parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/css-what/-/css-what-4.0.0.tgz">https://registry.npmjs.org/css-what/-/css-what-4.0.0.tgz</a></p>
<p>Path to dependency file: website_frontend/package.json</p>
<p>Path to vulnerable library: website_frontend/node_modules/css-what/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-12.2.8.tgz (Root Library)
- css-minimizer-webpack-plugin-3.0.2.tgz
- cssnano-5.0.8.tgz
- cssnano-preset-default-5.1.4.tgz
- postcss-svgo-5.0.2.tgz
- svgo-2.3.0.tgz
- css-select-3.1.2.tgz
- :x: **css-what-4.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Verseghy/website_frontend/commit/9aa2f4022cfc5aaab093eb3cc9c540a9bfc3eed1">9aa2f4022cfc5aaab093eb3cc9c540a9bfc3eed1</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The css-what package 4.0.0 through 5.0.0 for Node.js does not ensure that attribute parsing has Linear Time Complexity relative to the size of the input.
<p>Publish Date: 2021-05-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33587>CVE-2021-33587</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33587">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33587</a></p>
<p>Release Date: 2021-05-28</p>
<p>Fix Resolution: css-what - 5.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-33587 (High) detected in css-what-4.0.0.tgz - ## CVE-2021-33587 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>css-what-4.0.0.tgz</b></p></summary>
<p>a CSS selector parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/css-what/-/css-what-4.0.0.tgz">https://registry.npmjs.org/css-what/-/css-what-4.0.0.tgz</a></p>
<p>Path to dependency file: website_frontend/package.json</p>
<p>Path to vulnerable library: website_frontend/node_modules/css-what/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-12.2.8.tgz (Root Library)
- css-minimizer-webpack-plugin-3.0.2.tgz
- cssnano-5.0.8.tgz
- cssnano-preset-default-5.1.4.tgz
- postcss-svgo-5.0.2.tgz
- svgo-2.3.0.tgz
- css-select-3.1.2.tgz
- :x: **css-what-4.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Verseghy/website_frontend/commit/9aa2f4022cfc5aaab093eb3cc9c540a9bfc3eed1">9aa2f4022cfc5aaab093eb3cc9c540a9bfc3eed1</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The css-what package 4.0.0 through 5.0.0 for Node.js does not ensure that attribute parsing has Linear Time Complexity relative to the size of the input.
<p>Publish Date: 2021-05-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33587>CVE-2021-33587</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33587">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33587</a></p>
<p>Release Date: 2021-05-28</p>
<p>Fix Resolution: css-what - 5.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in css what tgz cve high severity vulnerability vulnerable library css what tgz a css selector parser library home page a href path to dependency file website frontend package json path to vulnerable library website frontend node modules css what package json dependency hierarchy build angular tgz root library css minimizer webpack plugin tgz cssnano tgz cssnano preset default tgz postcss svgo tgz svgo tgz css select tgz x css what tgz vulnerable library found in head commit a href found in base branch master vulnerability details the css what package through for node js does not ensure that attribute parsing has linear time complexity relative to the size of the input publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution css what step up your open source security game with whitesource | 0 |
280,130 | 21,194,888,319 | IssuesEvent | 2022-04-08 22:31:22 | deepfence/PacketStreamer | https://api.github.com/repos/deepfence/PacketStreamer | reopened | README - Add instructions to show live stream use cases | documentation | Show how to live stream traffic into various tools for detection purposes.
I.e. sensor --> receiver --> live stream | TOOL where TOOL = { Zeek, Suricata, Tshark, Moloch etc}
1. Suricata
2. Zeek
3. Tshark
4. Moloch | 1.0 | README - Add instructions to show live stream use cases - Show how to live stream traffic into various tools for detection purposes.
I.e. sensor --> receiver --> live stream | TOOL where TOOL = { Zeek, Suricata, Tshark, Moloch etc}
1. Suricata
2. Zeek
3. Tshark
4. Moloch | non_priority | readme add instructions to show live stream use cases show how to live stream traffic into various tools for detection purposes i e sensor receiver live stream tool where tool zeek suricata tshark moloch etc suricata zeek tshark moloch | 0 |
338,470 | 30,300,297,267 | IssuesEvent | 2023-07-10 05:06:21 | SWM-Cupid/jikting-backend | https://api.github.com/repos/SWM-Cupid/jikting-backend | opened | [SP-131] 팀 삭제 API 명세서 작성 | feature docs test | ## Jira Issue
[SP-131](https://soma-cupid.atlassian.net/browse/SP-131?atlOrigin=eyJpIjoiMDY1YjAxZTEyY2U3NGNlZWJiMjkwNmU5NWVjYTQxZDUiLCJwIjoiaiJ9)
## 요구사항
- [ ] 팀 삭제 성공 API 명세서 작성
- [ ] 팀 삭제 실패 API 명세서 작성 | 1.0 | [SP-131] 팀 삭제 API 명세서 작성 - ## Jira Issue
[SP-131](https://soma-cupid.atlassian.net/browse/SP-131?atlOrigin=eyJpIjoiMDY1YjAxZTEyY2U3NGNlZWJiMjkwNmU5NWVjYTQxZDUiLCJwIjoiaiJ9)
## 요구사항
- [ ] 팀 삭제 성공 API 명세서 작성
- [ ] 팀 삭제 실패 API 명세서 작성 | non_priority | 팀 삭제 api 명세서 작성 jira issue 요구사항 팀 삭제 성공 api 명세서 작성 팀 삭제 실패 api 명세서 작성 | 0 |
161,031 | 25,275,838,268 | IssuesEvent | 2022-11-16 12:33:33 | codestates-seb/seb40_main_035 | https://api.github.com/repos/codestates-seb/seb40_main_035 | opened | feat: 프로필 기본 정보란 컴포넌트 구현 | Design Frontend Feat | ## 💁 설명
마이페이지와 프로필 상세보기 페이지에서 사용되는 프로필 기본 정보란 컴포넌트 구현
## 📑 작업해야 할 내용
- [ ] 컴포넌트 마크업 및 스타일링
- [ ] props로 데이터 받아올 수 있도록 하기
## 🕰 예상 작업 시간
4h | 1.0 | feat: 프로필 기본 정보란 컴포넌트 구현 - ## 💁 설명
마이페이지와 프로필 상세보기 페이지에서 사용되는 프로필 기본 정보란 컴포넌트 구현
## 📑 작업해야 할 내용
- [ ] 컴포넌트 마크업 및 스타일링
- [ ] props로 데이터 받아올 수 있도록 하기
## 🕰 예상 작업 시간
4h | non_priority | feat 프로필 기본 정보란 컴포넌트 구현 💁 설명 마이페이지와 프로필 상세보기 페이지에서 사용되는 프로필 기본 정보란 컴포넌트 구현 📑 작업해야 할 내용 컴포넌트 마크업 및 스타일링 props로 데이터 받아올 수 있도록 하기 🕰 예상 작업 시간 | 0 |
54,703 | 23,319,773,632 | IssuesEvent | 2022-08-08 15:21:47 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | [Android][x86] System.Runtime.InteropServices.Tests.NFloatTests failed | arch-x86 area-System.Runtime.InteropServices os-android in-pr | There are the following failures in the `System.Runtime.InteropServices.Tests.NFloatTests` library test suite which are being hit on Android x86 leg in https://github.com/dotnet/runtime/pull/65551:
```
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Subtraction(left: -4567, right: 3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Subtraction" time="0.0140883" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -4570.1400001049042\nActual: -4570.14013671875]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Subtraction(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 244
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Subtraction(left: -4567.89111, right: 3.14568996)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Subtraction" time="0.0003036" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -4571.0368032455444\nActual: -4571.03662109375]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Subtraction(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 244
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Subtraction(left: 0, right: 3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Subtraction" time="0.0000064" result="Pass" />
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Subtraction(left: 4567, right: -3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Subtraction" time="0.0002445" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: 4570.1400001049042\nActual: 4570.14013671875]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Subtraction(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 244
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Subtraction(left: 4567.89111, right: -3.14568996)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Subtraction" time="0.000254" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: 4571.0368032455444\nActual: 4571.03662109375]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Subtraction(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 244
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Division(left: -4567, right: 3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Division" time="0.0005455" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -1454.4585501341485\nActual: -1454.45849609375]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Division(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 284
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Division(left: -4567.89111, right: 3.14568996)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Division" time="0.000232" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -1452.1110360937337\nActual: -1452.111083984375]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Division(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 284
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Division(left: 0, right: 3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Division" time="0.0000054" result="Pass" />
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Division(left: 4567, right: -3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Division" time="0.0002909" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -1454.4585501341485\nActual: -1454.45849609375]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Division(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 284
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Division(left: 4567.89111, right: -3.14568996)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Division" time="0.0002319" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -1452.1110360937337\nActual: -1452.111083984375]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Division(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 284
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Addition(left: -4567, right: 3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Addition" time="0.0005737" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -4563.8599998950958\nActual: -4563.85986328125]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Addition(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 224
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Addition(left: -4567.89111, right: 3.14568996)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Addition" time="0.0002292" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -4564.7454233169556\nActual: -4564.74560546875]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Addition(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 224
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Addition(left: 0, right: 3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Addition" time="0.0000053" result="Pass" />
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Addition(left: 4567, right: -3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Addition" time="0.0029769" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: 4563.8599998950958\nActual: 4563.85986328125]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Addition(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 224
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Addition(left: 4567.89111, right: -3.14568996)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Addition" time="0.0002373" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: 4564.7454233169556\nActual: 4564.74560546875]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Addition(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 224
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Multiply(left: -4567, right: 3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Multiply" time="0.0005585" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -14340.380479097366\nActual: -14340.380859375]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Multiply(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 264
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Multiply(left: -4567.89111, right: 3.14568996)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Multiply" time="0.0002354" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -14369.169233038556\nActual: -14369.1689453125]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Multiply(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 264
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Multiply(left: 0, right: 3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Multiply" time="0.0000054" result="Pass" />
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Multiply(left: 4567, right: -3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Multiply" time="0.0020525" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -14340.380479097366\nActual: -14340.380859375]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Multiply(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 264
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Multiply(left: 4567.89111, right: -3.14568996)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Multiply" time="0.0002333" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -14369.169233038556\nActual: -14369.1689453125]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Multiply(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 264
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
```
https://dev.azure.com/dnceng/public/_build/results?buildId=1620509&view=ms.vss-test-web.build-test-results-tab&runId=45058618&paneView=debug&resultId=166936
cc @steveisok @akoeplinger @tannergooding @vargaz | 1.0 | [Android][x86] System.Runtime.InteropServices.Tests.NFloatTests failed - There are the following failures in the `System.Runtime.InteropServices.Tests.NFloatTests` library test suite which are being hit on Android x86 leg in https://github.com/dotnet/runtime/pull/65551:
```
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Subtraction(left: -4567, right: 3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Subtraction" time="0.0140883" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -4570.1400001049042\nActual: -4570.14013671875]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Subtraction(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 244
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Subtraction(left: -4567.89111, right: 3.14568996)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Subtraction" time="0.0003036" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -4571.0368032455444\nActual: -4571.03662109375]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Subtraction(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 244
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Subtraction(left: 0, right: 3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Subtraction" time="0.0000064" result="Pass" />
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Subtraction(left: 4567, right: -3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Subtraction" time="0.0002445" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: 4570.1400001049042\nActual: 4570.14013671875]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Subtraction(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 244
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Subtraction(left: 4567.89111, right: -3.14568996)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Subtraction" time="0.000254" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: 4571.0368032455444\nActual: 4571.03662109375]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Subtraction(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 244
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Division(left: -4567, right: 3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Division" time="0.0005455" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -1454.4585501341485\nActual: -1454.45849609375]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Division(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 284
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Division(left: -4567.89111, right: 3.14568996)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Division" time="0.000232" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -1452.1110360937337\nActual: -1452.111083984375]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Division(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 284
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Division(left: 0, right: 3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Division" time="0.0000054" result="Pass" />
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Division(left: 4567, right: -3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Division" time="0.0002909" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -1454.4585501341485\nActual: -1454.45849609375]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Division(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 284
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Division(left: 4567.89111, right: -3.14568996)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Division" time="0.0002319" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -1452.1110360937337\nActual: -1452.111083984375]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Division(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 284
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Addition(left: -4567, right: 3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Addition" time="0.0005737" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -4563.8599998950958\nActual: -4563.85986328125]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Addition(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 224
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Addition(left: -4567.89111, right: 3.14568996)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Addition" time="0.0002292" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -4564.7454233169556\nActual: -4564.74560546875]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Addition(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 224
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Addition(left: 0, right: 3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Addition" time="0.0000053" result="Pass" />
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Addition(left: 4567, right: -3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Addition" time="0.0029769" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: 4563.8599998950958\nActual: 4563.85986328125]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Addition(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 224
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Addition(left: 4567.89111, right: -3.14568996)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Addition" time="0.0002373" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: 4564.7454233169556\nActual: 4564.74560546875]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Addition(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 224
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Multiply(left: -4567, right: 3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Multiply" time="0.0005585" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -14340.380479097366\nActual: -14340.380859375]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Multiply(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 264
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Multiply(left: -4567.89111, right: 3.14568996)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Multiply" time="0.0002354" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -14369.169233038556\nActual: -14369.1689453125]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Multiply(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 264
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Multiply(left: 0, right: 3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Multiply" time="0.0000054" result="Pass" />
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Multiply(left: 4567, right: -3.1400001)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Multiply" time="0.0020525" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -14340.380479097366\nActual: -14340.380859375]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Multiply(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 264
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
<test name="System.Runtime.InteropServices.Tests.NFloatTests.op_Multiply(left: 4567.89111, right: -3.14568996)" type="System.Runtime.InteropServices.Tests.NFloatTests" method="op_Multiply" time="0.0002333" result="Fail">
<failure exception-type="Xunit.Sdk.EqualException">
<message><![CDATA[Assert.Equal() Failure\nExpected: -14369.169233038556\nActual: -14369.1689453125]]></message>
<stack-trace><![CDATA[ at System.Runtime.InteropServices.Tests.NFloatTests.op_Multiply(Single left, Single right) in /_/src/libraries/System.Runtime.InteropServices/tests/System.Runtime.InteropServices.UnitTests/System/Runtime/InteropServices/NFloatTests.cs:line 264
at System.Reflection.RuntimeMethodInfo.InvokeWorker(Object obj, BindingFlags invokeAttr, Span`1 parameters)]]></stack-trace>
</failure>
</test>
```
https://dev.azure.com/dnceng/public/_build/results?buildId=1620509&view=ms.vss-test-web.build-test-results-tab&runId=45058618&paneView=debug&resultId=166936
cc @steveisok @akoeplinger @tannergooding @vargaz | non_priority | system runtime interopservices tests nfloattests failed there are the following failures in the system runtime interopservices tests nfloattests library test suite which are being hit on android leg in cdata at system runtime interopservices tests nfloattests op subtraction single left single right in src libraries system runtime interopservices tests system runtime interopservices unittests system runtime interopservices nfloattests cs line at system reflection runtimemethodinfo invokeworker object obj bindingflags invokeattr span parameters cdata at system runtime interopservices tests nfloattests op subtraction single left single right in src libraries system runtime interopservices tests system runtime interopservices unittests system runtime interopservices nfloattests cs line at system reflection runtimemethodinfo invokeworker object obj bindingflags invokeattr span parameters cdata at system runtime interopservices tests nfloattests op subtraction single left single right in src libraries system runtime interopservices tests system runtime interopservices unittests system runtime interopservices nfloattests cs line at system reflection runtimemethodinfo invokeworker object obj bindingflags invokeattr span parameters cdata at system runtime interopservices tests nfloattests op subtraction single left single right in src libraries system runtime interopservices tests system runtime interopservices unittests system runtime interopservices nfloattests cs line at system reflection runtimemethodinfo invokeworker object obj bindingflags invokeattr span parameters cdata at system runtime interopservices tests nfloattests op division single left single right in src libraries system runtime interopservices tests system runtime interopservices unittests system runtime interopservices nfloattests cs line at system reflection runtimemethodinfo invokeworker object obj bindingflags invokeattr span parameters cdata at system runtime interopservices tests nfloattests op division single left single right in src libraries system runtime interopservices tests system runtime interopservices unittests system runtime interopservices nfloattests cs line at system reflection runtimemethodinfo invokeworker object obj bindingflags invokeattr span parameters cdata at system runtime interopservices tests nfloattests op division single left single right in src libraries system runtime interopservices tests system runtime interopservices unittests system runtime interopservices nfloattests cs line at system reflection runtimemethodinfo invokeworker object obj bindingflags invokeattr span parameters cdata at system runtime interopservices tests nfloattests op division single left single right in src libraries system runtime interopservices tests system runtime interopservices unittests system runtime interopservices nfloattests cs line at system reflection runtimemethodinfo invokeworker object obj bindingflags invokeattr span parameters cdata at system runtime interopservices tests nfloattests op addition single left single right in src libraries system runtime interopservices tests system runtime interopservices unittests system runtime interopservices nfloattests cs line at system reflection runtimemethodinfo invokeworker object obj bindingflags invokeattr span parameters cdata at system runtime interopservices tests nfloattests op addition single left single right in src libraries system runtime interopservices tests system runtime interopservices unittests system runtime interopservices nfloattests cs line at system reflection runtimemethodinfo invokeworker object obj bindingflags invokeattr span parameters cdata at system runtime interopservices tests nfloattests op addition single left single right in src libraries system runtime interopservices tests system runtime interopservices unittests system runtime interopservices nfloattests cs line at system reflection runtimemethodinfo invokeworker object obj bindingflags invokeattr span parameters cdata at system runtime interopservices tests nfloattests op addition single left single right in src libraries system runtime interopservices tests system runtime interopservices unittests system runtime interopservices nfloattests cs line at system reflection runtimemethodinfo invokeworker object obj bindingflags invokeattr span parameters cdata at system runtime interopservices tests nfloattests op multiply single left single right in src libraries system runtime interopservices tests system runtime interopservices unittests system runtime interopservices nfloattests cs line at system reflection runtimemethodinfo invokeworker object obj bindingflags invokeattr span parameters cdata at system runtime interopservices tests nfloattests op multiply single left single right in src libraries system runtime interopservices tests system runtime interopservices unittests system runtime interopservices nfloattests cs line at system reflection runtimemethodinfo invokeworker object obj bindingflags invokeattr span parameters cdata at system runtime interopservices tests nfloattests op multiply single left single right in src libraries system runtime interopservices tests system runtime interopservices unittests system runtime interopservices nfloattests cs line at system reflection runtimemethodinfo invokeworker object obj bindingflags invokeattr span parameters cdata at system runtime interopservices tests nfloattests op multiply single left single right in src libraries system runtime interopservices tests system runtime interopservices unittests system runtime interopservices nfloattests cs line at system reflection runtimemethodinfo invokeworker object obj bindingflags invokeattr span parameters cc steveisok akoeplinger tannergooding vargaz | 0 |
139,834 | 12,880,622,349 | IssuesEvent | 2020-07-12 07:10:28 | fluttercandies/flutter_wechat_assets_picker | https://api.github.com/repos/fluttercandies/flutter_wechat_assets_picker | opened | [Contributors] Add your contributions. | documentation 📢EXTRA ATTENTION | Contributions are welcome for everyone who wants to improve this package. For who has already contribute to the package, you can add your contributions if you wish. | 1.0 | [Contributors] Add your contributions. - Contributions are welcome for everyone who wants to improve this package. For who has already contribute to the package, you can add your contributions if you wish. | non_priority | add your contributions contributions are welcome for everyone who wants to improve this package for who has already contribute to the package you can add your contributions if you wish | 0 |
171,760 | 13,247,412,464 | IssuesEvent | 2020-08-19 17:12:35 | nrwl/nx | https://api.github.com/repos/nrwl/nx | closed | Jest Paths to Modules failing when running tests | scope: testing tools type: bug | I have an NX workspace up and running, haven't had any trouble with it in some time. However recently I created a new app, and have some paths configured in it in ts.config.app.json (I have no choice but to use these paths):
```
paths: {
"core/*": ["apps/myapp/myapp-ui/src/app/core/*"],
"shared/*": ["apps/,myapp/myapp-ui/src/app/shared/*"],
"templates/*": ["apps/myapp/myapp-ui/src/app/templates/*"],
}
or
paths: {
"^core/(.*)": ["apps/myapp/myapp-ui/src/app/core/1$"],
...
}
```
etc. (and many other options tried).
It works fines, runs as expected, etc, until I try to test it (using Jest). Then it's all "modules not found".
I have tried configuring modulePaths, moduleNameMapper, etc. etc. in the jest.config that lives in the root of the app, which looks like this:
workspace
-- apps
----someapps
------myapp
------jest.config.js
Nothing works, the modules are never found. I originally suspected that the rootDir is not doing what I'd expect it to be doing, but by "breaking" the jest resolver, it traces out the rootDir in the console (it actually tells you, rootDir = etc/etc), so I know it's correct.
Any wisdom on this one would be greatly appreciated. I'm at a total brick wall here and I need to get these tests running. If I put the app in a vanilla angular 8 project, everything works fine.
Thanks in advance. I have looked elsewhere in the issues here, but there doesn't seem, to be any basic guidance insofar as, "this is how it resolves the rootDir, which means this is how you need to configure it." | 1.0 | Jest Paths to Modules failing when running tests - I have an NX workspace up and running, haven't had any trouble with it in some time. However recently I created a new app, and have some paths configured in it in ts.config.app.json (I have no choice but to use these paths):
```
paths: {
"core/*": ["apps/myapp/myapp-ui/src/app/core/*"],
"shared/*": ["apps/,myapp/myapp-ui/src/app/shared/*"],
"templates/*": ["apps/myapp/myapp-ui/src/app/templates/*"],
}
or
paths: {
"^core/(.*)": ["apps/myapp/myapp-ui/src/app/core/1$"],
...
}
```
etc. (and many other options tried).
It works fines, runs as expected, etc, until I try to test it (using Jest). Then it's all "modules not found".
I have tried configuring modulePaths, moduleNameMapper, etc. etc. in the jest.config that lives in the root of the app, which looks like this:
workspace
-- apps
----someapps
------myapp
------jest.config.js
Nothing works, the modules are never found. I originally suspected that the rootDir is not doing what I'd expect it to be doing, but by "breaking" the jest resolver, it traces out the rootDir in the console (it actually tells you, rootDir = etc/etc), so I know it's correct.
Any wisdom on this one would be greatly appreciated. I'm at a total brick wall here and I need to get these tests running. If I put the app in a vanilla angular 8 project, everything works fine.
Thanks in advance. I have looked elsewhere in the issues here, but there doesn't seem, to be any basic guidance insofar as, "this is how it resolves the rootDir, which means this is how you need to configure it." | non_priority | jest paths to modules failing when running tests i have an nx workspace up and running haven t had any trouble with it in some time however recently i created a new app and have some paths configured in it in ts config app json i have no choice but to use these paths paths core shared templates or paths core etc and many other options tried it works fines runs as expected etc until i try to test it using jest then it s all modules not found i have tried configuring modulepaths modulenamemapper etc etc in the jest config that lives in the root of the app which looks like this workspace apps someapps myapp jest config js nothing works the modules are never found i originally suspected that the rootdir is not doing what i d expect it to be doing but by breaking the jest resolver it traces out the rootdir in the console it actually tells you rootdir etc etc so i know it s correct any wisdom on this one would be greatly appreciated i m at a total brick wall here and i need to get these tests running if i put the app in a vanilla angular project everything works fine thanks in advance i have looked elsewhere in the issues here but there doesn t seem to be any basic guidance insofar as this is how it resolves the rootdir which means this is how you need to configure it | 0 |
6,303 | 9,308,456,875 | IssuesEvent | 2019-03-25 14:35:59 | brandon1roadgears/Interpreter-of-programming-language-of-Turing-Machine | https://api.github.com/repos/brandon1roadgears/Interpreter-of-programming-language-of-Turing-Machine | opened | Проверка работоспособности программы. | Testing process | # После завершения работы необходимо проверить, как программа решает те или инные задачи.
***
### (@goldmen4ik) Нам необходимо найти на просторах интернета около 10 задач c решением для машины тьюринга, чтобы проверить, способна ли она справиться с ними.
* ### Думаю этого ресурса будет достаточно: [https://infourok.ru/reshenie-zadach-mashina-tyuringa-2302088.html](url), Если есть варианты интереснее - отправить их сюда комментарием. | 1.0 | Проверка работоспособности программы. - # После завершения работы необходимо проверить, как программа решает те или инные задачи.
***
### (@goldmen4ik) Нам необходимо найти на просторах интернета около 10 задач c решением для машины тьюринга, чтобы проверить, способна ли она справиться с ними.
* ### Думаю этого ресурса будет достаточно: [https://infourok.ru/reshenie-zadach-mashina-tyuringa-2302088.html](url), Если есть варианты интереснее - отправить их сюда комментарием. | non_priority | проверка работоспособности программы после завершения работы необходимо проверить как программа решает те или инные задачи нам необходимо найти на просторах интернета около задач c решением для машины тьюринга чтобы проверить способна ли она справиться с ними думаю этого ресурса будет достаточно url если есть варианты интереснее отправить их сюда комментарием | 0 |
221,615 | 17,023,986,595 | IssuesEvent | 2021-07-03 04:55:57 | casbin-lua/lua-resty-casbin | https://api.github.com/repos/casbin-lua/lua-resty-casbin | closed | Move the Setup-OpenResty.md docs to this repo | documentation | Previously we had a docs here: https://github.com/casbin/lua-casbin/blob/master/Setup-OpenResty.md but now we have this repo. I think we can move that docs here now. | 1.0 | Move the Setup-OpenResty.md docs to this repo - Previously we had a docs here: https://github.com/casbin/lua-casbin/blob/master/Setup-OpenResty.md but now we have this repo. I think we can move that docs here now. | non_priority | move the setup openresty md docs to this repo previously we had a docs here but now we have this repo i think we can move that docs here now | 0 |
116,588 | 14,981,826,878 | IssuesEvent | 2021-01-28 15:17:25 | nhsuk/nhsuk-service-manual | https://api.github.com/repos/nhsuk/nhsuk-service-manual | closed | Synthesise research findings into actionable artefacts pt 2 [Journey map] | :clock10: days contribution design | ## What
We have gotten plenty of data from our series of research activities, but we need to funnel all that research data into useful information
## Why
This allows us to make sense of the data we have gathered and enables us to make informed decisions & actions
## How
We plan to move our generated behaviour groups through our as-is process to isolate consistent pain points, especially one which have clear evidence
## Relation
Relates to #685 | 1.0 | Synthesise research findings into actionable artefacts pt 2 [Journey map] - ## What
We have gotten plenty of data from our series of research activities, but we need to funnel all that research data into useful information
## Why
This allows us to make sense of the data we have gathered and enables us to make informed decisions & actions
## How
We plan to move our generated behaviour groups through our as-is process to isolate consistent pain points, especially one which have clear evidence
## Relation
Relates to #685 | non_priority | synthesise research findings into actionable artefacts pt what we have gotten plenty of data from our series of research activities but we need to funnel all that research data into useful information why this allows us to make sense of the data we have gathered and enables us to make informed decisions actions how we plan to move our generated behaviour groups through our as is process to isolate consistent pain points especially one which have clear evidence relation relates to | 0 |
332,797 | 29,493,453,088 | IssuesEvent | 2023-06-02 15:02:47 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | roachtest: failover/chaos/read-write failed | C-test-failure O-robot O-roachtest branch-master release-blocker T-kv | roachtest.failover/chaos/read-write [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/10356406?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/10356406?buildTab=artifacts#/failover/chaos/read-write) on master @ [bf25b7bf93a6b8e57557813957da263389796bb4](https://github.com/cockroachdb/cockroach/commits/bf25b7bf93a6b8e57557813957da263389796bb4):
```
test artifacts and logs in: /artifacts/failover/chaos/read-write/run_1
(cluster.go:1995).Start: ~ COCKROACH_CONNECT_TIMEOUT=1200 ./cockroach sql --url 'postgres://root@localhost:26257?sslmode=disable' -e "CREATE SCHEDULE IF NOT EXISTS test_only_backup FOR BACKUP INTO 'gs://cockroachdb-backup-testing/roachprod-scheduled-backups/teamcity-10356406-1685683233-66-n10cpu4/1685716020684784515?AUTH=implicit' RECURRING '*/15 * * * *' FULL BACKUP '@hourly' WITH SCHEDULE OPTIONS first_run = 'now'"
ERROR: cannot dial server.
Is the server running?
If the server is running, check --host client-side and --advertise server-side.
timeout: context deadline exceeded
Failed running "sql": COMMAND_PROBLEM: exit status 1
(cluster.go:2095).Run: output in run_140857.260155216_n10_cockroach-workload-r: ./cockroach workload run kv --read-percent 50 --write-seq R0 --duration 45m --concurrency 256 --max-rate 8192 --timeout 1m --tolerate-errors --histograms=perf/stats.json {pgurl:1-2} returned: context canceled
(monitor.go:127).Wait: monitor failure: monitor task failed: t.Fatal() was called
(cluster.go:2095).Run: cluster.RunE: context canceled
(cluster.go:2095).Run: cluster.RunE: context canceled
(cluster.go:2095).Run: cluster.RunE: context canceled
(cluster.go:2095).Run: cluster.RunE: context canceled
```
<p>Parameters: <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_encrypted=false</code>
, <code>ROACHTEST_fs=ext4</code>
, <code>ROACHTEST_localSSD=false</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/kv-triage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*failover/chaos/read-write.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 2.0 | roachtest: failover/chaos/read-write failed - roachtest.failover/chaos/read-write [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/10356406?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/10356406?buildTab=artifacts#/failover/chaos/read-write) on master @ [bf25b7bf93a6b8e57557813957da263389796bb4](https://github.com/cockroachdb/cockroach/commits/bf25b7bf93a6b8e57557813957da263389796bb4):
```
test artifacts and logs in: /artifacts/failover/chaos/read-write/run_1
(cluster.go:1995).Start: ~ COCKROACH_CONNECT_TIMEOUT=1200 ./cockroach sql --url 'postgres://root@localhost:26257?sslmode=disable' -e "CREATE SCHEDULE IF NOT EXISTS test_only_backup FOR BACKUP INTO 'gs://cockroachdb-backup-testing/roachprod-scheduled-backups/teamcity-10356406-1685683233-66-n10cpu4/1685716020684784515?AUTH=implicit' RECURRING '*/15 * * * *' FULL BACKUP '@hourly' WITH SCHEDULE OPTIONS first_run = 'now'"
ERROR: cannot dial server.
Is the server running?
If the server is running, check --host client-side and --advertise server-side.
timeout: context deadline exceeded
Failed running "sql": COMMAND_PROBLEM: exit status 1
(cluster.go:2095).Run: output in run_140857.260155216_n10_cockroach-workload-r: ./cockroach workload run kv --read-percent 50 --write-seq R0 --duration 45m --concurrency 256 --max-rate 8192 --timeout 1m --tolerate-errors --histograms=perf/stats.json {pgurl:1-2} returned: context canceled
(monitor.go:127).Wait: monitor failure: monitor task failed: t.Fatal() was called
(cluster.go:2095).Run: cluster.RunE: context canceled
(cluster.go:2095).Run: cluster.RunE: context canceled
(cluster.go:2095).Run: cluster.RunE: context canceled
(cluster.go:2095).Run: cluster.RunE: context canceled
```
<p>Parameters: <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_encrypted=false</code>
, <code>ROACHTEST_fs=ext4</code>
, <code>ROACHTEST_localSSD=false</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/kv-triage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*failover/chaos/read-write.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| non_priority | roachtest failover chaos read write failed roachtest failover chaos read write with on master test artifacts and logs in artifacts failover chaos read write run cluster go start cockroach connect timeout cockroach sql url postgres root localhost sslmode disable e create schedule if not exists test only backup for backup into gs cockroachdb backup testing roachprod scheduled backups teamcity auth implicit recurring full backup hourly with schedule options first run now error cannot dial server is the server running if the server is running check host client side and advertise server side timeout context deadline exceeded failed running sql command problem exit status cluster go run output in run cockroach workload r cockroach workload run kv read percent write seq duration concurrency max rate timeout tolerate errors histograms perf stats json pgurl returned context canceled monitor go wait monitor failure monitor task failed t fatal was called cluster go run cluster rune context canceled cluster go run cluster rune context canceled cluster go run cluster rune context canceled cluster go run cluster rune context canceled parameters roachtest cloud gce roachtest cpu roachtest encrypted false roachtest fs roachtest localssd false roachtest ssd help see see cc cockroachdb kv triage | 0 |
81,201 | 23,412,583,317 | IssuesEvent | 2022-08-12 19:18:37 | elastic/elastic-agent-shipper | https://api.github.com/repos/elastic/elastic-agent-shipper | opened | Build 29 for main with status FAILURE | Team:Elastic-Agent-Data-Plane ci-reported automation build-failures |
## :broken_heart: Tests Failed
<!-- BUILD BADGES-->
> _the below badges are clickable and redirect to their specific view in the CI or DOCS_
[](https://fleet-ci.elastic.co/blue/organizations/jenkins/elastic-agent-shipper-mbp%2Fmain/detail/main/29//pipeline) [](https://fleet-ci.elastic.co/blue/organizations/jenkins/elastic-agent-shipper-mbp%2Fmain/detail/main/29//tests) [](https://fleet-ci.elastic.co/blue/organizations/jenkins/elastic-agent-shipper-mbp%2Fmain/detail/main/29//changes) [](https://fleet-ci.elastic.co/blue/organizations/jenkins/elastic-agent-shipper-mbp%2Fmain/detail/main/29//artifacts) [](http://elastic-agent-shipper_null.docs-preview.app.elstc.co/diff) [](https://ci-stats.elastic.co/app/apm/services/fleet-ci/transactions/view?rangeFrom=2022-08-12T18:58:06.418Z&rangeTo=2022-08-12T19:18:06.418Z&transactionName=elastic-agent-shipper-mbp/main&transactionType=job&latencyAggregationType=avg&traceId=e2722b7c2924e6b233751d054006535d&transactionId=5f526bf081fc7588)
<!-- BUILD SUMMARY-->
<details><summary>Expand to view the summary</summary>
<p>
#### Build stats
* Start Time: 2022-08-12T19:08:06.418+0000
* Duration: 10 min 21 sec
#### Test stats :test_tube:
| Test | Results |
| ------------ | :-----------------------------: |
| Failed | 3 |
| Passed | 37 |
| Skipped | 0 |
| Total | 40 |
</p>
</details>
<!-- TEST RESULTS IF ANY-->
### Test errors [](https://fleet-ci.elastic.co/blue/organizations/jenkins/elastic-agent-shipper-mbp%2Fmain/detail/main/29//tests)
<details><summary>Expand to view the tests failures</summary><p>
##### `Test / Matrix - PLATFORM = "ubuntu-20.04 && immutable" / Test / TestPublish/should_return_validation_errors/no_timestamp – github.com/elastic/elastic-agent-shipper/server`
<ul>
<details><summary>Expand to view the error details</summary><p>
```
Failed
```
</p></details>
<details><summary>Expand to view the stacktrace</summary><p>
```
=== RUN TestPublish/should_return_validation_errors/no_timestamp
server_test.go:243:
Error Trace: server_test.go:243
Error: Not equal:
expected: "timestamp: proto:\u00a0invalid nil Timestamp"
actual : "timestamp: proto: invalid nil Timestamp"
Diff:
--- Expected
+++ Actual
@@ -1 +1 @@
-timestamp: proto: invalid nil Timestamp
+timestamp: proto: invalid nil Timestamp
Test: TestPublish/should_return_validation_errors/no_timestamp
--- FAIL: TestPublish/should_return_validation_errors/no_timestamp (0.00s)
```
</p></details>
</ul>
##### `Test / Matrix - PLATFORM = "ubuntu-20.04 && immutable" / Test / TestPublish/should_return_validation_errors – github.com/elastic/elastic-agent-shipper/server`
<ul>
<details><summary>Expand to view the error details</summary><p>
```
Failed
```
</p></details>
<details><summary>Expand to view the stacktrace</summary><p>
```
=== RUN TestPublish/should_return_validation_errors
--- FAIL: TestPublish/should_return_validation_errors (0.00s)
```
</p></details>
</ul>
##### `Test / Matrix - PLATFORM = "ubuntu-20.04 && immutable" / Test / TestPublish – github.com/elastic/elastic-agent-shipper/server`
<ul>
<details><summary>Expand to view the error details</summary><p>
```
Failed
```
</p></details>
<details><summary>Expand to view the stacktrace</summary><p>
```
=== RUN TestPublish
--- FAIL: TestPublish (0.01s)
```
</p></details>
</ul>
</p></details>
<!-- STEPS ERRORS IF ANY -->
### Steps errors [](https://fleet-ci.elastic.co/blue/organizations/jenkins/elastic-agent-shipper-mbp%2Fmain/detail/main/29//pipeline)
<details><summary>Expand to view the steps failures</summary>
<p>
##### `Running Go tests`
<ul>
<li>Took 0 min 7 sec . View more details <a href="https://fleet-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/elastic-agent-shipper-mbp/pipelines/main/runs/29/steps/263/log/?start=0">here</a></li>
<li>Description: <code>gotestsum --format testname --junitfile junit-report.xml -- -v ./...</code></l1>
</ul>
</p>
</details>
| 1.0 | Build 29 for main with status FAILURE -
## :broken_heart: Tests Failed
<!-- BUILD BADGES-->
> _the below badges are clickable and redirect to their specific view in the CI or DOCS_
[](https://fleet-ci.elastic.co/blue/organizations/jenkins/elastic-agent-shipper-mbp%2Fmain/detail/main/29//pipeline) [](https://fleet-ci.elastic.co/blue/organizations/jenkins/elastic-agent-shipper-mbp%2Fmain/detail/main/29//tests) [](https://fleet-ci.elastic.co/blue/organizations/jenkins/elastic-agent-shipper-mbp%2Fmain/detail/main/29//changes) [](https://fleet-ci.elastic.co/blue/organizations/jenkins/elastic-agent-shipper-mbp%2Fmain/detail/main/29//artifacts) [](http://elastic-agent-shipper_null.docs-preview.app.elstc.co/diff) [](https://ci-stats.elastic.co/app/apm/services/fleet-ci/transactions/view?rangeFrom=2022-08-12T18:58:06.418Z&rangeTo=2022-08-12T19:18:06.418Z&transactionName=elastic-agent-shipper-mbp/main&transactionType=job&latencyAggregationType=avg&traceId=e2722b7c2924e6b233751d054006535d&transactionId=5f526bf081fc7588)
<!-- BUILD SUMMARY-->
<details><summary>Expand to view the summary</summary>
<p>
#### Build stats
* Start Time: 2022-08-12T19:08:06.418+0000
* Duration: 10 min 21 sec
#### Test stats :test_tube:
| Test | Results |
| ------------ | :-----------------------------: |
| Failed | 3 |
| Passed | 37 |
| Skipped | 0 |
| Total | 40 |
</p>
</details>
<!-- TEST RESULTS IF ANY-->
### Test errors [](https://fleet-ci.elastic.co/blue/organizations/jenkins/elastic-agent-shipper-mbp%2Fmain/detail/main/29//tests)
<details><summary>Expand to view the tests failures</summary><p>
##### `Test / Matrix - PLATFORM = "ubuntu-20.04 && immutable" / Test / TestPublish/should_return_validation_errors/no_timestamp – github.com/elastic/elastic-agent-shipper/server`
<ul>
<details><summary>Expand to view the error details</summary><p>
```
Failed
```
</p></details>
<details><summary>Expand to view the stacktrace</summary><p>
```
=== RUN TestPublish/should_return_validation_errors/no_timestamp
server_test.go:243:
Error Trace: server_test.go:243
Error: Not equal:
expected: "timestamp: proto:\u00a0invalid nil Timestamp"
actual : "timestamp: proto: invalid nil Timestamp"
Diff:
--- Expected
+++ Actual
@@ -1 +1 @@
-timestamp: proto: invalid nil Timestamp
+timestamp: proto: invalid nil Timestamp
Test: TestPublish/should_return_validation_errors/no_timestamp
--- FAIL: TestPublish/should_return_validation_errors/no_timestamp (0.00s)
```
</p></details>
</ul>
##### `Test / Matrix - PLATFORM = "ubuntu-20.04 && immutable" / Test / TestPublish/should_return_validation_errors – github.com/elastic/elastic-agent-shipper/server`
<ul>
<details><summary>Expand to view the error details</summary><p>
```
Failed
```
</p></details>
<details><summary>Expand to view the stacktrace</summary><p>
```
=== RUN TestPublish/should_return_validation_errors
--- FAIL: TestPublish/should_return_validation_errors (0.00s)
```
</p></details>
</ul>
##### `Test / Matrix - PLATFORM = "ubuntu-20.04 && immutable" / Test / TestPublish – github.com/elastic/elastic-agent-shipper/server`
<ul>
<details><summary>Expand to view the error details</summary><p>
```
Failed
```
</p></details>
<details><summary>Expand to view the stacktrace</summary><p>
```
=== RUN TestPublish
--- FAIL: TestPublish (0.01s)
```
</p></details>
</ul>
</p></details>
<!-- STEPS ERRORS IF ANY -->
### Steps errors [](https://fleet-ci.elastic.co/blue/organizations/jenkins/elastic-agent-shipper-mbp%2Fmain/detail/main/29//pipeline)
<details><summary>Expand to view the steps failures</summary>
<p>
##### `Running Go tests`
<ul>
<li>Took 0 min 7 sec . View more details <a href="https://fleet-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/elastic-agent-shipper-mbp/pipelines/main/runs/29/steps/263/log/?start=0">here</a></li>
<li>Description: <code>gotestsum --format testname --junitfile junit-report.xml -- -v ./...</code></l1>
</ul>
</p>
</details>
| non_priority | build for main with status failure broken heart tests failed the below badges are clickable and redirect to their specific view in the ci or docs expand to view the summary build stats start time duration min sec test stats test tube test results failed passed skipped total test errors expand to view the tests failures test matrix platform ubuntu immutable test testpublish should return validation errors no timestamp – github com elastic elastic agent shipper server expand to view the error details failed expand to view the stacktrace run testpublish should return validation errors no timestamp server test go error trace server test go error not equal expected timestamp proto nil timestamp actual timestamp proto invalid nil timestamp diff expected actual timestamp proto invalid nil timestamp timestamp proto invalid nil timestamp test testpublish should return validation errors no timestamp fail testpublish should return validation errors no timestamp test matrix platform ubuntu immutable test testpublish should return validation errors – github com elastic elastic agent shipper server expand to view the error details failed expand to view the stacktrace run testpublish should return validation errors fail testpublish should return validation errors test matrix platform ubuntu immutable test testpublish – github com elastic elastic agent shipper server expand to view the error details failed expand to view the stacktrace run testpublish fail testpublish steps errors expand to view the steps failures running go tests took min sec view more details a href description gotestsum format testname junitfile junit report xml v | 0 |
174,268 | 13,464,863,837 | IssuesEvent | 2020-09-09 19:53:35 | golang/go | https://api.github.com/repos/golang/go | opened | cmd/go: in tests, populate go.sum files and reduce usage of -mod=mod | NeedsFix Testing | This issue acts as a TODO for a number of comments raised in review of [CL 251881](https://go-review.googlesource.com/c/go/+/251881), which enables `-mod=readonly` by default for #40278. Two broad issues should be fixed in the `cmd/go` integration tests.
First, `-mod=mod` is used in a lot of places with `go list` or `go build`. We should make the tests follow more idiomatic usage. If something is missing from `go.mod` or `go.sum`, we should run `go get -d`, `go mod tidy`, or `go mod download` first. The following tests need changes. There are probably more.
* `mod_doc`
* `mod_download`.
* `mod_invalid_version`
* `mod_list`
* `mod_load_badzip`
* `mod_replace`
* `mod_replace_gopkgin`
* `mod_require_exclude`
* `mod_sumdb_golang`
Second, many tests fail without `-mod=mod` because the test archive doesn't include a `go.sum` file. I'd rather not include literal `go.sum` files in tests, since they'll make tests more difficult to write and act as change detectors. Instead, we should have a command or sequence of commands run at the beginning of a test that fills in missing sums without modifying `go.mod`. Something like:
```
cp go.mod go.mod.orig
go get -d ./...
cmp go.mod go.mod.orig
```
If this turns out to be too repetitive, we may want to add a `script_test.go` command to shorten it.
The following tests need changes. Again, there are probably more.
* `mod_list_dir`
* `mod_list_replace_dir`
* `mod_list_upgrade`
* `mod_load_badmod`
* `mod_modinfo`
| 1.0 | cmd/go: in tests, populate go.sum files and reduce usage of -mod=mod - This issue acts as a TODO for a number of comments raised in review of [CL 251881](https://go-review.googlesource.com/c/go/+/251881), which enables `-mod=readonly` by default for #40278. Two broad issues should be fixed in the `cmd/go` integration tests.
First, `-mod=mod` is used in a lot of places with `go list` or `go build`. We should make the tests follow more idiomatic usage. If something is missing from `go.mod` or `go.sum`, we should run `go get -d`, `go mod tidy`, or `go mod download` first. The following tests need changes. There are probably more.
* `mod_doc`
* `mod_download`.
* `mod_invalid_version`
* `mod_list`
* `mod_load_badzip`
* `mod_replace`
* `mod_replace_gopkgin`
* `mod_require_exclude`
* `mod_sumdb_golang`
Second, many tests fail without `-mod=mod` because the test archive doesn't include a `go.sum` file. I'd rather not include literal `go.sum` files in tests, since they'll make tests more difficult to write and act as change detectors. Instead, we should have a command or sequence of commands run at the beginning of a test that fills in missing sums without modifying `go.mod`. Something like:
```
cp go.mod go.mod.orig
go get -d ./...
cmp go.mod go.mod.orig
```
If this turns out to be too repetitive, we may want to add a `script_test.go` command to shorten it.
The following tests need changes. Again, there are probably more.
* `mod_list_dir`
* `mod_list_replace_dir`
* `mod_list_upgrade`
* `mod_load_badmod`
* `mod_modinfo`
| non_priority | cmd go in tests populate go sum files and reduce usage of mod mod this issue acts as a todo for a number of comments raised in review of which enables mod readonly by default for two broad issues should be fixed in the cmd go integration tests first mod mod is used in a lot of places with go list or go build we should make the tests follow more idiomatic usage if something is missing from go mod or go sum we should run go get d go mod tidy or go mod download first the following tests need changes there are probably more mod doc mod download mod invalid version mod list mod load badzip mod replace mod replace gopkgin mod require exclude mod sumdb golang second many tests fail without mod mod because the test archive doesn t include a go sum file i d rather not include literal go sum files in tests since they ll make tests more difficult to write and act as change detectors instead we should have a command or sequence of commands run at the beginning of a test that fills in missing sums without modifying go mod something like cp go mod go mod orig go get d cmp go mod go mod orig if this turns out to be too repetitive we may want to add a script test go command to shorten it the following tests need changes again there are probably more mod list dir mod list replace dir mod list upgrade mod load badmod mod modinfo | 0 |
230,308 | 25,461,907,781 | IssuesEvent | 2022-11-24 20:31:37 | rsoreq/cwa-server | https://api.github.com/repos/rsoreq/cwa-server | opened | CVE-2022-41946 (Medium) detected in postgresql-42.2.13.jar | security vulnerability | ## CVE-2022-41946 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>postgresql-42.2.13.jar</b></p></summary>
<p>PostgreSQL JDBC Driver Postgresql</p>
<p>Library home page: <a href="https://jdbc.postgresql.org">https://jdbc.postgresql.org</a></p>
<p>Path to dependency file: /common/persistence/pom.xml</p>
<p>Path to vulnerable library: /epository/org/postgresql/postgresql/42.2.13/postgresql-42.2.13.jar,/epository/org/postgresql/postgresql/42.2.13/postgresql-42.2.13.jar,/epository/org/postgresql/postgresql/42.2.13/postgresql-42.2.13.jar</p>
<p>
Dependency Hierarchy:
- :x: **postgresql-42.2.13.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
pgjdbc is an open source postgresql JDBC Driver. In affected versions a prepared statement using either `PreparedStatement.setText(int, InputStream)` or `PreparedStatemet.setBytea(int, InputStream)` will create a temporary file if the InputStream is larger than 2k. This will create a temporary file which is readable by other users on Unix like systems, but not MacOS. On Unix like systems, the system's temporary directory is shared between all users on that system. Because of this, when files and directories are written into this directory they are, by default, readable by other users on that same system. This vulnerability does not allow other users to overwrite the contents of these directories or files. This is purely an information disclosure vulnerability. Because certain JDK file system APIs were only added in JDK 1.7, this this fix is dependent upon the version of the JDK you are using. Java 1.7 and higher users: this vulnerability is fixed in 4.5.0. Java 1.6 and lower users: no patch is available. If you are unable to patch, or are stuck running on Java 1.6, specifying the java.io.tmpdir system environment variable to a directory that is exclusively owned by the executing user will mitigate this vulnerability.
<p>Publish Date: 2022-11-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41946>CVE-2022-41946</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/pgjdbc/pgjdbc/security/advisories/GHSA-562r-vg33-8x8h">https://github.com/pgjdbc/pgjdbc/security/advisories/GHSA-562r-vg33-8x8h</a></p>
<p>Release Date: 2022-11-23</p>
<p>Fix Resolution: 42.2.26.jre6</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| True | CVE-2022-41946 (Medium) detected in postgresql-42.2.13.jar - ## CVE-2022-41946 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>postgresql-42.2.13.jar</b></p></summary>
<p>PostgreSQL JDBC Driver Postgresql</p>
<p>Library home page: <a href="https://jdbc.postgresql.org">https://jdbc.postgresql.org</a></p>
<p>Path to dependency file: /common/persistence/pom.xml</p>
<p>Path to vulnerable library: /epository/org/postgresql/postgresql/42.2.13/postgresql-42.2.13.jar,/epository/org/postgresql/postgresql/42.2.13/postgresql-42.2.13.jar,/epository/org/postgresql/postgresql/42.2.13/postgresql-42.2.13.jar</p>
<p>
Dependency Hierarchy:
- :x: **postgresql-42.2.13.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
pgjdbc is an open source postgresql JDBC Driver. In affected versions a prepared statement using either `PreparedStatement.setText(int, InputStream)` or `PreparedStatemet.setBytea(int, InputStream)` will create a temporary file if the InputStream is larger than 2k. This will create a temporary file which is readable by other users on Unix like systems, but not MacOS. On Unix like systems, the system's temporary directory is shared between all users on that system. Because of this, when files and directories are written into this directory they are, by default, readable by other users on that same system. This vulnerability does not allow other users to overwrite the contents of these directories or files. This is purely an information disclosure vulnerability. Because certain JDK file system APIs were only added in JDK 1.7, this this fix is dependent upon the version of the JDK you are using. Java 1.7 and higher users: this vulnerability is fixed in 4.5.0. Java 1.6 and lower users: no patch is available. If you are unable to patch, or are stuck running on Java 1.6, specifying the java.io.tmpdir system environment variable to a directory that is exclusively owned by the executing user will mitigate this vulnerability.
<p>Publish Date: 2022-11-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41946>CVE-2022-41946</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/pgjdbc/pgjdbc/security/advisories/GHSA-562r-vg33-8x8h">https://github.com/pgjdbc/pgjdbc/security/advisories/GHSA-562r-vg33-8x8h</a></p>
<p>Release Date: 2022-11-23</p>
<p>Fix Resolution: 42.2.26.jre6</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| non_priority | cve medium detected in postgresql jar cve medium severity vulnerability vulnerable library postgresql jar postgresql jdbc driver postgresql library home page a href path to dependency file common persistence pom xml path to vulnerable library epository org postgresql postgresql postgresql jar epository org postgresql postgresql postgresql jar epository org postgresql postgresql postgresql jar dependency hierarchy x postgresql jar vulnerable library found in base branch master vulnerability details pgjdbc is an open source postgresql jdbc driver in affected versions a prepared statement using either preparedstatement settext int inputstream or preparedstatemet setbytea int inputstream will create a temporary file if the inputstream is larger than this will create a temporary file which is readable by other users on unix like systems but not macos on unix like systems the system s temporary directory is shared between all users on that system because of this when files and directories are written into this directory they are by default readable by other users on that same system this vulnerability does not allow other users to overwrite the contents of these directories or files this is purely an information disclosure vulnerability because certain jdk file system apis were only added in jdk this this fix is dependent upon the version of the jdk you are using java and higher users this vulnerability is fixed in java and lower users no patch is available if you are unable to patch or are stuck running on java specifying the java io tmpdir system environment variable to a directory that is exclusively owned by the executing user will mitigate this vulnerability publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution check this box to open an automated fix pr | 0 |
334,443 | 24,419,486,539 | IssuesEvent | 2022-10-05 18:57:20 | transit-analytics-lab/spur | https://api.github.com/repos/transit-analytics-lab/spur | closed | Simple example with working data (Toronto's Sheppard line) | documentation | Package a set of required data files to simulate a basic 2-way subway schedule based on GTFS data. | 1.0 | Simple example with working data (Toronto's Sheppard line) - Package a set of required data files to simulate a basic 2-way subway schedule based on GTFS data. | non_priority | simple example with working data toronto s sheppard line package a set of required data files to simulate a basic way subway schedule based on gtfs data | 0 |
784 | 3,226,546,946 | IssuesEvent | 2015-10-10 11:15:16 | afscrome/IronVelocity | https://api.github.com/repos/afscrome/IronVelocity | opened | NVelocity compatibility extensions | enhancement nvelocity compatibility | Currently there are a few NVelocity specific features embedded in the core, we should pull these out and allow these to be extensions instead.
* [ ] `to_squote`
* [ ] `to_quote`
* [ ] dictionary strings
* [ ] special handling for properties of object that is typeof(ENUM) | True | NVelocity compatibility extensions - Currently there are a few NVelocity specific features embedded in the core, we should pull these out and allow these to be extensions instead.
* [ ] `to_squote`
* [ ] `to_quote`
* [ ] dictionary strings
* [ ] special handling for properties of object that is typeof(ENUM) | non_priority | nvelocity compatibility extensions currently there are a few nvelocity specific features embedded in the core we should pull these out and allow these to be extensions instead to squote to quote dictionary strings special handling for properties of object that is typeof enum | 0 |
47,257 | 11,992,050,230 | IssuesEvent | 2020-04-08 09:26:06 | syncthing/syncthing | https://api.github.com/repos/syncthing/syncthing | closed | Remove macOS 32 bit builds | build | As of currently our minimum macOS requirement is 10.10, which does not support any 32 bit hardware. The last macOS to support 32 bit hardware was 10.6, and our binaries haven't worked there for years. Hence there is no point in the 32 bit build.
(Issue for visibility and to document the reasoning & decision, not that it's specifically actionable.)
(ref #6516) | 1.0 | Remove macOS 32 bit builds - As of currently our minimum macOS requirement is 10.10, which does not support any 32 bit hardware. The last macOS to support 32 bit hardware was 10.6, and our binaries haven't worked there for years. Hence there is no point in the 32 bit build.
(Issue for visibility and to document the reasoning & decision, not that it's specifically actionable.)
(ref #6516) | non_priority | remove macos bit builds as of currently our minimum macos requirement is which does not support any bit hardware the last macos to support bit hardware was and our binaries haven t worked there for years hence there is no point in the bit build issue for visibility and to document the reasoning decision not that it s specifically actionable ref | 0 |
21,095 | 14,361,011,820 | IssuesEvent | 2020-11-30 17:38:10 | servo/servo | https://api.github.com/repos/servo/servo | closed | WPT nightly sync is broken | A-infrastructure I-bustage | ```
Switched to a new branch 'wpt_update'
7:17.98 vcs ERROR fatal: bad object f2282e8294bb649c075b273f373423f9b215a16c
Error running mach:
['update-wpt', '--sync', '--no-upstream', '--patch']
The error occurred in code that was called by the mach command. This is either
a bug in the called code itself or in the way that mach is calling it.
You should consider filing a bug for this issue.
If filing a bug, please include the full output of mach, including this error
message.
The details of the failure are as follows:
CalledProcessError: Command '['git', 'show', '-s', '--format=format:%an\n%ae\n%B', 'f2282e8294bb649c075b273f373423f9b215a16c']' returned non-zero exit status 128
File "/Users/servo/buildbot/slave/mac-nightly/build/python/servo/testing_commands.py", line 479, in update_wpt
return run_globals["update_tests"](**kwargs)
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/update.py", line 25, in update_tests
rv = update.run_update(logger, **kwargs)
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/update/__init__.py", line 26, in run_update
return updater.run()
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/update/update.py", line 180, in run
rv = update_runner.run()
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/update/base.py", line 61, in run
rv = step(self.logger).run(step_index, self.state)
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/update/base.py", line 32, in run
self.create(state)
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/update/update.py", line 75, in create
runner.run()
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/update/base.py", line 61, in run
rv = step(self.logger).run(step_index, self.state)
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/update/base.py", line 32, in run
self.create(state)
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/update/sync.py", line 128, in create
state.sync["branch"])
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/update/tree.py", line 252, in get_remote_sha1
return self.commit_cls(self, sha1)
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/update/tree.py", line 392, in __init__
self.author, self.email, self.message = self._get_meta()
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/update/tree.py", line 404, in _get_meta
author, email, message = self.git("show", "-s", "--format=format:%an\n%ae\n%B", self.sha1).split("\n", 2)
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/vcs.py", line 36, in inner
return func(command_line, stderr=subprocess.STDOUT, **proc_kwargs)
File "/usr/local/Cellar/python@2/2.7.15_1/Frameworks/Python.framework/Versions/2.7/lib/python2.7/subprocess.py", line 223, in check_output
raise CalledProcessError(retcode, cmd, output=output)
fatal: No such remote: sync-fork
HEAD is now at 834d3193a2 Auto merge of #21780 - jdm:ndk15upgrade, r=asajeffrey
Switched to branch 'master'
``` | 1.0 | WPT nightly sync is broken - ```
Switched to a new branch 'wpt_update'
7:17.98 vcs ERROR fatal: bad object f2282e8294bb649c075b273f373423f9b215a16c
Error running mach:
['update-wpt', '--sync', '--no-upstream', '--patch']
The error occurred in code that was called by the mach command. This is either
a bug in the called code itself or in the way that mach is calling it.
You should consider filing a bug for this issue.
If filing a bug, please include the full output of mach, including this error
message.
The details of the failure are as follows:
CalledProcessError: Command '['git', 'show', '-s', '--format=format:%an\n%ae\n%B', 'f2282e8294bb649c075b273f373423f9b215a16c']' returned non-zero exit status 128
File "/Users/servo/buildbot/slave/mac-nightly/build/python/servo/testing_commands.py", line 479, in update_wpt
return run_globals["update_tests"](**kwargs)
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/update.py", line 25, in update_tests
rv = update.run_update(logger, **kwargs)
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/update/__init__.py", line 26, in run_update
return updater.run()
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/update/update.py", line 180, in run
rv = update_runner.run()
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/update/base.py", line 61, in run
rv = step(self.logger).run(step_index, self.state)
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/update/base.py", line 32, in run
self.create(state)
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/update/update.py", line 75, in create
runner.run()
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/update/base.py", line 61, in run
rv = step(self.logger).run(step_index, self.state)
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/update/base.py", line 32, in run
self.create(state)
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/update/sync.py", line 128, in create
state.sync["branch"])
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/update/tree.py", line 252, in get_remote_sha1
return self.commit_cls(self, sha1)
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/update/tree.py", line 392, in __init__
self.author, self.email, self.message = self._get_meta()
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/update/tree.py", line 404, in _get_meta
author, email, message = self.git("show", "-s", "--format=format:%an\n%ae\n%B", self.sha1).split("\n", 2)
File "/Users/servo/buildbot/slave/mac-nightly/build/tests/wpt/web-platform-tests/tools/wptrunner/wptrunner/vcs.py", line 36, in inner
return func(command_line, stderr=subprocess.STDOUT, **proc_kwargs)
File "/usr/local/Cellar/python@2/2.7.15_1/Frameworks/Python.framework/Versions/2.7/lib/python2.7/subprocess.py", line 223, in check_output
raise CalledProcessError(retcode, cmd, output=output)
fatal: No such remote: sync-fork
HEAD is now at 834d3193a2 Auto merge of #21780 - jdm:ndk15upgrade, r=asajeffrey
Switched to branch 'master'
``` | non_priority | wpt nightly sync is broken switched to a new branch wpt update vcs error fatal bad object error running mach the error occurred in code that was called by the mach command this is either a bug in the called code itself or in the way that mach is calling it you should consider filing a bug for this issue if filing a bug please include the full output of mach including this error message the details of the failure are as follows calledprocesserror command returned non zero exit status file users servo buildbot slave mac nightly build python servo testing commands py line in update wpt return run globals kwargs file users servo buildbot slave mac nightly build tests wpt update py line in update tests rv update run update logger kwargs file users servo buildbot slave mac nightly build tests wpt update init py line in run update return updater run file users servo buildbot slave mac nightly build tests wpt web platform tests tools wptrunner wptrunner update update py line in run rv update runner run file users servo buildbot slave mac nightly build tests wpt web platform tests tools wptrunner wptrunner update base py line in run rv step self logger run step index self state file users servo buildbot slave mac nightly build tests wpt web platform tests tools wptrunner wptrunner update base py line in run self create state file users servo buildbot slave mac nightly build tests wpt web platform tests tools wptrunner wptrunner update update py line in create runner run file users servo buildbot slave mac nightly build tests wpt web platform tests tools wptrunner wptrunner update base py line in run rv step self logger run step index self state file users servo buildbot slave mac nightly build tests wpt web platform tests tools wptrunner wptrunner update base py line in run self create state file users servo buildbot slave mac nightly build tests wpt web platform tests tools wptrunner wptrunner update sync py line in create state sync file users servo buildbot slave mac nightly build tests wpt web platform tests tools wptrunner wptrunner update tree py line in get remote return self commit cls self file users servo buildbot slave mac nightly build tests wpt web platform tests tools wptrunner wptrunner update tree py line in init self author self email self message self get meta file users servo buildbot slave mac nightly build tests wpt web platform tests tools wptrunner wptrunner update tree py line in get meta author email message self git show s format format an n ae n b self split n file users servo buildbot slave mac nightly build tests wpt web platform tests tools wptrunner wptrunner vcs py line in inner return func command line stderr subprocess stdout proc kwargs file usr local cellar python frameworks python framework versions lib subprocess py line in check output raise calledprocesserror retcode cmd output output fatal no such remote sync fork head is now at auto merge of jdm r asajeffrey switched to branch master | 0 |
345,469 | 24,861,290,683 | IssuesEvent | 2022-10-27 08:29:20 | mamba-org/mamba | https://api.github.com/repos/mamba-org/mamba | reopened | bug: ~/.mambarc do not work | documentation | I installed the latest version of `Mambaforge` and set up a configuration file identical to my stable `.condarc` file. While creating a new environment or anything else for that matter, this file is not respected at all, even though this should have been according to [this](https://mamba.readthedocs.io/en/latest/user_guide/configuration.html).
## Reproducible setup
Used configuration file
```yaml
channels: ### the list of conda channels to include for relevant operations
- defaults
- conda-forge
channel_priority: strict ### with strict channel priority, packages in lower priority channels are not considered if a package with the same name appears in a higher priority channel
create_default_packages: ### packages that are by default added to a newly created environments
- python>=3.7
always_yes: false ### automatically choose the 'yes' option whenever asked to proceed with a conda operation
auto_activate_base: false ### automatically activate the base environment during shell initialization
add_pip_as_python_dependency: true ## add pip, wheel, and setuptools as dependencies of Python
```
Used command
```bash
mamba create --name test
```
This should try to create a new environment with python version >= 3.7. And that did not happen, and an environment got created with no package and without python itself.
## Workaround
Just renaming the file from `~/.mambarc` to `~/.condarc` solves the issue. | 1.0 | bug: ~/.mambarc do not work - I installed the latest version of `Mambaforge` and set up a configuration file identical to my stable `.condarc` file. While creating a new environment or anything else for that matter, this file is not respected at all, even though this should have been according to [this](https://mamba.readthedocs.io/en/latest/user_guide/configuration.html).
## Reproducible setup
Used configuration file
```yaml
channels: ### the list of conda channels to include for relevant operations
- defaults
- conda-forge
channel_priority: strict ### with strict channel priority, packages in lower priority channels are not considered if a package with the same name appears in a higher priority channel
create_default_packages: ### packages that are by default added to a newly created environments
- python>=3.7
always_yes: false ### automatically choose the 'yes' option whenever asked to proceed with a conda operation
auto_activate_base: false ### automatically activate the base environment during shell initialization
add_pip_as_python_dependency: true ## add pip, wheel, and setuptools as dependencies of Python
```
Used command
```bash
mamba create --name test
```
This should try to create a new environment with python version >= 3.7. And that did not happen, and an environment got created with no package and without python itself.
## Workaround
Just renaming the file from `~/.mambarc` to `~/.condarc` solves the issue. | non_priority | bug mambarc do not work i installed the latest version of mambaforge and set up a configuration file identical to my stable condarc file while creating a new environment or anything else for that matter this file is not respected at all even though this should have been according to reproducible setup used configuration file yaml channels the list of conda channels to include for relevant operations defaults conda forge channel priority strict with strict channel priority packages in lower priority channels are not considered if a package with the same name appears in a higher priority channel create default packages packages that are by default added to a newly created environments python always yes false automatically choose the yes option whenever asked to proceed with a conda operation auto activate base false automatically activate the base environment during shell initialization add pip as python dependency true add pip wheel and setuptools as dependencies of python used command bash mamba create name test this should try to create a new environment with python version and that did not happen and an environment got created with no package and without python itself workaround just renaming the file from mambarc to condarc solves the issue | 0 |
101,125 | 30,879,532,796 | IssuesEvent | 2023-08-03 16:29:24 | microsoft/PowerToys | https://api.github.com/repos/microsoft/PowerToys | closed | Build a DSC Resource for configuring PowerToys | Area-Quality Area-Build | ### Description of the new feature / enhancement
I would like a PowerShell DSC Resource for configuring PowerToys to my preferences.
The [WinGet](https://github.com/microsoft/winget-cli) team has been working on [DSC Resources](https://github.com/microsoft/winget-cli/issues/2697) for WinGet.
In response to:
* https://github.com/microsoft/winget-cli/issues/2845
The [WinGet](https://github.com/microsoft/winget-cli) team will draft a PR for a configuration file in the PowerToys repository as we work on automated configuration.
### Scenario when this would be used?
When I want to use PowerShell DSC to configure an environment, I would like to be able to apply the configuration for PowerToys in that environment.
### Supporting information
Related to:
* https://github.com/microsoft/winget-cli/issues/2845
[Desired State Configuration v3](https://devblogs.microsoft.com/powershell/powershell-openssh-team-investments-for-2023/#desired-state-configuration-v3) | 1.0 | Build a DSC Resource for configuring PowerToys - ### Description of the new feature / enhancement
I would like a PowerShell DSC Resource for configuring PowerToys to my preferences.
The [WinGet](https://github.com/microsoft/winget-cli) team has been working on [DSC Resources](https://github.com/microsoft/winget-cli/issues/2697) for WinGet.
In response to:
* https://github.com/microsoft/winget-cli/issues/2845
The [WinGet](https://github.com/microsoft/winget-cli) team will draft a PR for a configuration file in the PowerToys repository as we work on automated configuration.
### Scenario when this would be used?
When I want to use PowerShell DSC to configure an environment, I would like to be able to apply the configuration for PowerToys in that environment.
### Supporting information
Related to:
* https://github.com/microsoft/winget-cli/issues/2845
[Desired State Configuration v3](https://devblogs.microsoft.com/powershell/powershell-openssh-team-investments-for-2023/#desired-state-configuration-v3) | non_priority | build a dsc resource for configuring powertoys description of the new feature enhancement i would like a powershell dsc resource for configuring powertoys to my preferences the team has been working on for winget in response to the team will draft a pr for a configuration file in the powertoys repository as we work on automated configuration scenario when this would be used when i want to use powershell dsc to configure an environment i would like to be able to apply the configuration for powertoys in that environment supporting information related to | 0 |
375,347 | 26,159,247,690 | IssuesEvent | 2022-12-31 08:18:20 | dqdq4197/BitFolio-app | https://api.github.com/repos/dqdq4197/BitFolio-app | opened | Troubleshooting 기록. | documentation | 1. firebase > 15.*v 를 포함한 패키지 빌드 시 나타나는 에러
```bash
!] The following Swift pods cannot yet be integrated as static libraries:
The Swift pod `FirebaseCoreInternal` depends upon `GoogleUtilities`, which does not define modules. To opt into those targets generating module maps (which is necessary to import them from Swift when building as static libraries), you may set `use_modular_headers!` globally in your Podfile, or specify `:modular_headers => true` for particular dependencies.
```
임시 해결. https://github.com/invertase/react-native-firebase/issues/6332#issuecomment-1172950523
| 1.0 | Troubleshooting 기록. - 1. firebase > 15.*v 를 포함한 패키지 빌드 시 나타나는 에러
```bash
!] The following Swift pods cannot yet be integrated as static libraries:
The Swift pod `FirebaseCoreInternal` depends upon `GoogleUtilities`, which does not define modules. To opt into those targets generating module maps (which is necessary to import them from Swift when building as static libraries), you may set `use_modular_headers!` globally in your Podfile, or specify `:modular_headers => true` for particular dependencies.
```
임시 해결. https://github.com/invertase/react-native-firebase/issues/6332#issuecomment-1172950523
| non_priority | troubleshooting 기록 firebase v 를 포함한 패키지 빌드 시 나타나는 에러 bash the following swift pods cannot yet be integrated as static libraries the swift pod firebasecoreinternal depends upon googleutilities which does not define modules to opt into those targets generating module maps which is necessary to import them from swift when building as static libraries you may set use modular headers globally in your podfile or specify modular headers true for particular dependencies 임시 해결 | 0 |
294,823 | 22,163,609,690 | IssuesEvent | 2022-06-04 22:04:51 | TomSchimansky/CustomTkinter | https://api.github.com/repos/TomSchimansky/CustomTkinter | closed | Cannot compile exe with pyinstaller (Windows 7) | bug documentation | When using pyinstaller, pyinstaller cannot package customtkinter file

s | 1.0 | Cannot compile exe with pyinstaller (Windows 7) - When using pyinstaller, pyinstaller cannot package customtkinter file

s | non_priority | cannot compile exe with pyinstaller windows when using pyinstaller pyinstaller cannot package customtkinter file s | 0 |
301,332 | 22,748,040,709 | IssuesEvent | 2022-07-07 10:54:33 | jOOQ/jOOQ | https://api.github.com/repos/jOOQ/jOOQ | closed | Manual inline converter examples could use <![CDATA[ .. ]]> instead of xml entities | T: Enhancement C: Documentation P: Medium R: Wontfix E: All Editions | Instead of:
```xml
<!-- Associate that custom type with your inline converter. -->
<converter>org.jooq.Converter.ofNullable(
Integer.class, MyEnum.class,
i -> MyEnum.values()[i], MyEnum::ordinal
)</converter>
```
Do this:
```xml
<!-- Associate that custom type with your inline converter. -->
<converter><![CDATA[org.jooq.Converter.ofNullable(
Integer.class, MyEnum.class,
i -> MyEnum.values()[i], MyEnum::ordinal
)]]></converter>
``` | 1.0 | Manual inline converter examples could use <![CDATA[ .. ]]> instead of xml entities - Instead of:
```xml
<!-- Associate that custom type with your inline converter. -->
<converter>org.jooq.Converter.ofNullable(
Integer.class, MyEnum.class,
i -> MyEnum.values()[i], MyEnum::ordinal
)</converter>
```
Do this:
```xml
<!-- Associate that custom type with your inline converter. -->
<converter><![CDATA[org.jooq.Converter.ofNullable(
Integer.class, MyEnum.class,
i -> MyEnum.values()[i], MyEnum::ordinal
)]]></converter>
``` | non_priority | manual inline converter examples could use instead of xml entities instead of xml org jooq converter ofnullable integer class myenum class i gt myenum values myenum ordinal do this xml cdata org jooq converter ofnullable integer class myenum class i myenum values myenum ordinal | 0 |
100,143 | 21,178,217,439 | IssuesEvent | 2022-04-08 04:03:53 | withfig/fig | https://api.github.com/repos/withfig/fig | closed | Documentation: CONTRIBUTING.md refers to a withfig/docs repository, which apparently does not exist. | type:bug codebase:docs awaiting user reply | ### Sanity checks
- [X] I have searched [github.com/withfig/fig/issues](https://github.com/withfig/fig/issues?q=) and there are no duplicates of my issue
- [X] I have run `fig doctor` in the affected terminal session
- [ ] I have typed 'git ' and included a screenshot of the Debugger (click the Fig icon in the macOS menu bar)
### Issue Details
### Description:
https://github.com/withfig/fig/blob/main/CONTRIBUTING.md refers to https://github.com/withfig/docs, which leads to a 404 page.
### Environment
```bash
Not applicable.
```
| 1.0 | Documentation: CONTRIBUTING.md refers to a withfig/docs repository, which apparently does not exist. - ### Sanity checks
- [X] I have searched [github.com/withfig/fig/issues](https://github.com/withfig/fig/issues?q=) and there are no duplicates of my issue
- [X] I have run `fig doctor` in the affected terminal session
- [ ] I have typed 'git ' and included a screenshot of the Debugger (click the Fig icon in the macOS menu bar)
### Issue Details
### Description:
https://github.com/withfig/fig/blob/main/CONTRIBUTING.md refers to https://github.com/withfig/docs, which leads to a 404 page.
### Environment
```bash
Not applicable.
```
| non_priority | documentation contributing md refers to a withfig docs repository which apparently does not exist sanity checks i have searched and there are no duplicates of my issue i have run fig doctor in the affected terminal session i have typed git and included a screenshot of the debugger click the fig icon in the macos menu bar issue details description refers to which leads to a page environment bash not applicable | 0 |
237,013 | 19,590,343,316 | IssuesEvent | 2022-01-05 12:13:53 | apache/pulsar | https://api.github.com/repos/apache/pulsar | opened | Flaky-test: ReplicatorSubscriptionTest.testGetReplicatedSubscriptionStatus | flaky-tests | <!---
Instructions for reporting a flaky test using this issue template:
1. Replace [test class] in title and body with the test class name
2. Replace [test method] in title and body with the test method that failed. Multiple methods are flaky, remove the content that refers to the test method.
3. Replace "url here" with a url to an example failure. In the Github Actions workflow run logs, you can right click on the line number to copy a link to the line. Example of such url is https://github.com/apache/pulsar/pull/8892/checks?check_run_id=1531075794#step:9:377 . The logs are available for a limited amount of time (usually for a few weeks).
4. Replace "relevant parts of the exception stacktrace here" with the a few lines of the stack trace that shows at least the exception message and the line of test code where the stacktrace occurred.
5. Replace "full exception stacktrace here" with the full exception stacktrace from logs. This section will be hidden by default.
6. Remove all unused fields / content to unclutter the reported issue. Remove this comment too.
-->
ReplicatorSubscriptionTest class is flaky. The testGetReplicatedSubscriptionStatus test method fails sporadically.
[example failure](https://github.com/apache/pulsar/runs/4713066229?check_suite_focus=true#step:9:4385)
```
Error: Tests run: 14, Failures: 6, Errors: 0, Skipped: 8, Time elapsed: 21.02 s <<< FAILURE! - in org.apache.pulsar.broker.service.ReplicatorSubscriptionTest
Error: testGetReplicatedSubscriptionStatus(org.apache.pulsar.broker.service.ReplicatorSubscriptionTest) Time elapsed: 0.127 s <<< FAILURE!
org.apache.pulsar.client.admin.PulsarAdminException$ServerSideErrorException: HTTP 500 Internal Server Error
at org.apache.pulsar.client.admin.internal.BaseResource.getApiException(BaseResource.java:223)
at org.apache.pulsar.client.admin.internal.BaseResource$1.failed(BaseResource.java:134)
at org.glassfish.jersey.client.JerseyInvocation$1.failed(JerseyInvocation.java:882)
at org.glassfish.jersey.client.JerseyInvocation$1.completed(JerseyInvocation.java:863)
at org.glassfish.jersey.client.ClientRuntime.processResponse(ClientRuntime.java:229)
at org.glassfish.jersey.client.ClientRuntime.access$200(ClientRuntime.java:62)
at org.glassfish.jersey.client.ClientRuntime$2.lambda$response$0(ClientRuntime.java:173)
at org.glassfish.jersey.internal.Errors$1.call(Errors.java:248)
at org.glassfish.jersey.internal.Errors$1.call(Errors.java:244)
at org.glassfish.jersey.internal.Errors.process(Errors.java:292)
at org.glassfish.jersey.internal.Errors.process(Errors.java:274)
at org.glassfish.jersey.internal.Errors.process(Errors.java:244)
at org.glassfish.jersey.process.internal.RequestScope.runInScope(RequestScope.java:288)
at org.glassfish.jersey.client.ClientRuntime$2.response(ClientRuntime.java:173)
at org.apache.pulsar.client.admin.internal.http.AsyncHttpConnector.lambda$apply$1(AsyncHttpConnector.java:228)
at java.base/java.util.concurrent.CompletableFuture.uniWhenComplete(CompletableFuture.java:859)
at java.base/java.util.concurrent.CompletableFuture$UniWhenComplete.tryFire(CompletableFuture.java:837)
at java.base/java.util.concurrent.CompletableFuture.postComplete(CompletableFuture.java:506)
at java.base/java.util.concurrent.CompletableFuture.complete(CompletableFuture.java:2073)
at org.apache.pulsar.client.admin.internal.http.AsyncHttpConnector.lambda$retryOperation$4(AsyncHttpConnector.java:270)
at java.base/java.util.concurrent.CompletableFuture.uniWhenComplete(CompletableFuture.java:859)
at java.base/java.util.concurrent.CompletableFuture$UniWhenComplete.tryFire(CompletableFuture.java:837)
at java.base/java.util.concurrent.CompletableFuture.postComplete(CompletableFuture.java:506)
at java.base/java.util.concurrent.CompletableFuture.complete(CompletableFuture.java:2073)
at org.asynchttpclient.netty.NettyResponseFuture.loadContent(NettyResponseFuture.java:222)
at org.asynchttpclient.netty.NettyResponseFuture.done(NettyResponseFuture.java:257)
at org.asynchttpclient.netty.handler.AsyncHttpClientHandler.finishUpdate(AsyncHttpClientHandler.java:241)
at org.asynchttpclient.netty.handler.HttpHandler.handleChunk(HttpHandler.java:114)
at org.asynchttpclient.netty.handler.HttpHandler.handleRead(HttpHandler.java:143)
at org.asynchttpclient.netty.handler.AsyncHttpClientHandler.channelRead(AsyncHttpClientHandler.java:78)
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:379)
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:365)
at io.netty.channel.AbstractChannelHandlerContext.fireChannelRead(AbstractChannelHandlerContext.java:357)
at io.netty.handler.codec.MessageToMessageDecoder.channelRead(MessageToMessageDecoder.java:103)
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:379)
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:365)
at io.netty.channel.AbstractChannelHandlerContext.fireChannelRead(AbstractChannelHandlerContext.java:357)
at io.netty.channel.CombinedChannelDuplexHandler$DelegatingChannelHandlerContext.fireChannelRead(CombinedChannelDuplexHandler.java:436)
at io.netty.handler.codec.ByteToMessageDecoder.fireChannelRead(ByteToMessageDecoder.java:324)
at io.netty.handler.codec.ByteToMessageDecoder.channelRead(ByteToMessageDecoder.java:296)
at io.netty.channel.CombinedChannelDuplexHandler.channelRead(CombinedChannelDuplexHandler.java:251)
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:379)
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:365)
at io.netty.channel.AbstractChannelHandlerContext.fireChannelRead(AbstractChannelHandlerContext.java:357)
at io.netty.channel.DefaultChannelPipeline$HeadContext.channelRead(DefaultChannelPipeline.java:1410)
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:379)
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:365)
at io.netty.channel.DefaultChannelPipeline.fireChannelRead(DefaultChannelPipeline.java:919)
at io.netty.channel.nio.AbstractNioByteChannel$NioByteUnsafe.read(AbstractNioByteChannel.java:166)
at io.netty.channel.nio.NioEventLoop.processSelectedKey(NioEventLoop.java:722)
at io.netty.channel.nio.NioEventLoop.processSelectedKeysOptimized(NioEventLoop.java:658)
at io.netty.channel.nio.NioEventLoop.processSelectedKeys(NioEventLoop.java:584)
at io.netty.channel.nio.NioEventLoop.run(NioEventLoop.java:496)
at io.netty.util.concurrent.SingleThreadEventExecutor$4.run(SingleThreadEventExecutor.java:986)
at io.netty.util.internal.ThreadExecutorMap$2.run(ThreadExecutorMap.java:74)
at io.netty.util.concurrent.FastThreadLocalRunnable.run(FastThreadLocalRunnable.java:30)
at java.base/java.lang.Thread.run(Thread.java:829)
Caused by: javax.ws.rs.InternalServerErrorException: HTTP 500 Internal Server Error
at org.glassfish.jersey.client.JerseyInvocation.convertToException(JerseyInvocation.java:960)
at org.glassfish.jersey.client.JerseyInvocation.access$700(JerseyInvocation.java:82)
... 54 more
```
| 1.0 | Flaky-test: ReplicatorSubscriptionTest.testGetReplicatedSubscriptionStatus - <!---
Instructions for reporting a flaky test using this issue template:
1. Replace [test class] in title and body with the test class name
2. Replace [test method] in title and body with the test method that failed. Multiple methods are flaky, remove the content that refers to the test method.
3. Replace "url here" with a url to an example failure. In the Github Actions workflow run logs, you can right click on the line number to copy a link to the line. Example of such url is https://github.com/apache/pulsar/pull/8892/checks?check_run_id=1531075794#step:9:377 . The logs are available for a limited amount of time (usually for a few weeks).
4. Replace "relevant parts of the exception stacktrace here" with the a few lines of the stack trace that shows at least the exception message and the line of test code where the stacktrace occurred.
5. Replace "full exception stacktrace here" with the full exception stacktrace from logs. This section will be hidden by default.
6. Remove all unused fields / content to unclutter the reported issue. Remove this comment too.
-->
ReplicatorSubscriptionTest class is flaky. The testGetReplicatedSubscriptionStatus test method fails sporadically.
[example failure](https://github.com/apache/pulsar/runs/4713066229?check_suite_focus=true#step:9:4385)
```
Error: Tests run: 14, Failures: 6, Errors: 0, Skipped: 8, Time elapsed: 21.02 s <<< FAILURE! - in org.apache.pulsar.broker.service.ReplicatorSubscriptionTest
Error: testGetReplicatedSubscriptionStatus(org.apache.pulsar.broker.service.ReplicatorSubscriptionTest) Time elapsed: 0.127 s <<< FAILURE!
org.apache.pulsar.client.admin.PulsarAdminException$ServerSideErrorException: HTTP 500 Internal Server Error
at org.apache.pulsar.client.admin.internal.BaseResource.getApiException(BaseResource.java:223)
at org.apache.pulsar.client.admin.internal.BaseResource$1.failed(BaseResource.java:134)
at org.glassfish.jersey.client.JerseyInvocation$1.failed(JerseyInvocation.java:882)
at org.glassfish.jersey.client.JerseyInvocation$1.completed(JerseyInvocation.java:863)
at org.glassfish.jersey.client.ClientRuntime.processResponse(ClientRuntime.java:229)
at org.glassfish.jersey.client.ClientRuntime.access$200(ClientRuntime.java:62)
at org.glassfish.jersey.client.ClientRuntime$2.lambda$response$0(ClientRuntime.java:173)
at org.glassfish.jersey.internal.Errors$1.call(Errors.java:248)
at org.glassfish.jersey.internal.Errors$1.call(Errors.java:244)
at org.glassfish.jersey.internal.Errors.process(Errors.java:292)
at org.glassfish.jersey.internal.Errors.process(Errors.java:274)
at org.glassfish.jersey.internal.Errors.process(Errors.java:244)
at org.glassfish.jersey.process.internal.RequestScope.runInScope(RequestScope.java:288)
at org.glassfish.jersey.client.ClientRuntime$2.response(ClientRuntime.java:173)
at org.apache.pulsar.client.admin.internal.http.AsyncHttpConnector.lambda$apply$1(AsyncHttpConnector.java:228)
at java.base/java.util.concurrent.CompletableFuture.uniWhenComplete(CompletableFuture.java:859)
at java.base/java.util.concurrent.CompletableFuture$UniWhenComplete.tryFire(CompletableFuture.java:837)
at java.base/java.util.concurrent.CompletableFuture.postComplete(CompletableFuture.java:506)
at java.base/java.util.concurrent.CompletableFuture.complete(CompletableFuture.java:2073)
at org.apache.pulsar.client.admin.internal.http.AsyncHttpConnector.lambda$retryOperation$4(AsyncHttpConnector.java:270)
at java.base/java.util.concurrent.CompletableFuture.uniWhenComplete(CompletableFuture.java:859)
at java.base/java.util.concurrent.CompletableFuture$UniWhenComplete.tryFire(CompletableFuture.java:837)
at java.base/java.util.concurrent.CompletableFuture.postComplete(CompletableFuture.java:506)
at java.base/java.util.concurrent.CompletableFuture.complete(CompletableFuture.java:2073)
at org.asynchttpclient.netty.NettyResponseFuture.loadContent(NettyResponseFuture.java:222)
at org.asynchttpclient.netty.NettyResponseFuture.done(NettyResponseFuture.java:257)
at org.asynchttpclient.netty.handler.AsyncHttpClientHandler.finishUpdate(AsyncHttpClientHandler.java:241)
at org.asynchttpclient.netty.handler.HttpHandler.handleChunk(HttpHandler.java:114)
at org.asynchttpclient.netty.handler.HttpHandler.handleRead(HttpHandler.java:143)
at org.asynchttpclient.netty.handler.AsyncHttpClientHandler.channelRead(AsyncHttpClientHandler.java:78)
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:379)
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:365)
at io.netty.channel.AbstractChannelHandlerContext.fireChannelRead(AbstractChannelHandlerContext.java:357)
at io.netty.handler.codec.MessageToMessageDecoder.channelRead(MessageToMessageDecoder.java:103)
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:379)
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:365)
at io.netty.channel.AbstractChannelHandlerContext.fireChannelRead(AbstractChannelHandlerContext.java:357)
at io.netty.channel.CombinedChannelDuplexHandler$DelegatingChannelHandlerContext.fireChannelRead(CombinedChannelDuplexHandler.java:436)
at io.netty.handler.codec.ByteToMessageDecoder.fireChannelRead(ByteToMessageDecoder.java:324)
at io.netty.handler.codec.ByteToMessageDecoder.channelRead(ByteToMessageDecoder.java:296)
at io.netty.channel.CombinedChannelDuplexHandler.channelRead(CombinedChannelDuplexHandler.java:251)
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:379)
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:365)
at io.netty.channel.AbstractChannelHandlerContext.fireChannelRead(AbstractChannelHandlerContext.java:357)
at io.netty.channel.DefaultChannelPipeline$HeadContext.channelRead(DefaultChannelPipeline.java:1410)
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:379)
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:365)
at io.netty.channel.DefaultChannelPipeline.fireChannelRead(DefaultChannelPipeline.java:919)
at io.netty.channel.nio.AbstractNioByteChannel$NioByteUnsafe.read(AbstractNioByteChannel.java:166)
at io.netty.channel.nio.NioEventLoop.processSelectedKey(NioEventLoop.java:722)
at io.netty.channel.nio.NioEventLoop.processSelectedKeysOptimized(NioEventLoop.java:658)
at io.netty.channel.nio.NioEventLoop.processSelectedKeys(NioEventLoop.java:584)
at io.netty.channel.nio.NioEventLoop.run(NioEventLoop.java:496)
at io.netty.util.concurrent.SingleThreadEventExecutor$4.run(SingleThreadEventExecutor.java:986)
at io.netty.util.internal.ThreadExecutorMap$2.run(ThreadExecutorMap.java:74)
at io.netty.util.concurrent.FastThreadLocalRunnable.run(FastThreadLocalRunnable.java:30)
at java.base/java.lang.Thread.run(Thread.java:829)
Caused by: javax.ws.rs.InternalServerErrorException: HTTP 500 Internal Server Error
at org.glassfish.jersey.client.JerseyInvocation.convertToException(JerseyInvocation.java:960)
at org.glassfish.jersey.client.JerseyInvocation.access$700(JerseyInvocation.java:82)
... 54 more
```
| non_priority | flaky test replicatorsubscriptiontest testgetreplicatedsubscriptionstatus instructions for reporting a flaky test using this issue template replace in title and body with the test class name replace in title and body with the test method that failed multiple methods are flaky remove the content that refers to the test method replace url here with a url to an example failure in the github actions workflow run logs you can right click on the line number to copy a link to the line example of such url is the logs are available for a limited amount of time usually for a few weeks replace relevant parts of the exception stacktrace here with the a few lines of the stack trace that shows at least the exception message and the line of test code where the stacktrace occurred replace full exception stacktrace here with the full exception stacktrace from logs this section will be hidden by default remove all unused fields content to unclutter the reported issue remove this comment too replicatorsubscriptiontest class is flaky the testgetreplicatedsubscriptionstatus test method fails sporadically error tests run failures errors skipped time elapsed s failure in org apache pulsar broker service replicatorsubscriptiontest error testgetreplicatedsubscriptionstatus org apache pulsar broker service replicatorsubscriptiontest time elapsed s failure org apache pulsar client admin pulsaradminexception serversideerrorexception http internal server error at org apache pulsar client admin internal baseresource getapiexception baseresource java at org apache pulsar client admin internal baseresource failed baseresource java at org glassfish jersey client jerseyinvocation failed jerseyinvocation java at org glassfish jersey client jerseyinvocation completed jerseyinvocation java at org glassfish jersey client clientruntime processresponse clientruntime java at org glassfish jersey client clientruntime access clientruntime java at org glassfish jersey client clientruntime lambda response clientruntime java at org glassfish jersey internal errors call errors java at org glassfish jersey internal errors call errors java at org glassfish jersey internal errors process errors java at org glassfish jersey internal errors process errors java at org glassfish jersey internal errors process errors java at org glassfish jersey process internal requestscope runinscope requestscope java at org glassfish jersey client clientruntime response clientruntime java at org apache pulsar client admin internal http asynchttpconnector lambda apply asynchttpconnector java at java base java util concurrent completablefuture uniwhencomplete completablefuture java at java base java util concurrent completablefuture uniwhencomplete tryfire completablefuture java at java base java util concurrent completablefuture postcomplete completablefuture java at java base java util concurrent completablefuture complete completablefuture java at org apache pulsar client admin internal http asynchttpconnector lambda retryoperation asynchttpconnector java at java base java util concurrent completablefuture uniwhencomplete completablefuture java at java base java util concurrent completablefuture uniwhencomplete tryfire completablefuture java at java base java util concurrent completablefuture postcomplete completablefuture java at java base java util concurrent completablefuture complete completablefuture java at org asynchttpclient netty nettyresponsefuture loadcontent nettyresponsefuture java at org asynchttpclient netty nettyresponsefuture done nettyresponsefuture java at org asynchttpclient netty handler asynchttpclienthandler finishupdate asynchttpclienthandler java at org asynchttpclient netty handler httphandler handlechunk httphandler java at org asynchttpclient netty handler httphandler handleread httphandler java at org asynchttpclient netty handler asynchttpclienthandler channelread asynchttpclienthandler java at io netty channel abstractchannelhandlercontext invokechannelread abstractchannelhandlercontext java at io netty channel abstractchannelhandlercontext invokechannelread abstractchannelhandlercontext java at io netty channel abstractchannelhandlercontext firechannelread abstractchannelhandlercontext java at io netty handler codec messagetomessagedecoder channelread messagetomessagedecoder java at io netty channel abstractchannelhandlercontext invokechannelread abstractchannelhandlercontext java at io netty channel abstractchannelhandlercontext invokechannelread abstractchannelhandlercontext java at io netty channel abstractchannelhandlercontext firechannelread abstractchannelhandlercontext java at io netty channel combinedchannelduplexhandler delegatingchannelhandlercontext firechannelread combinedchannelduplexhandler java at io netty handler codec bytetomessagedecoder firechannelread bytetomessagedecoder java at io netty handler codec bytetomessagedecoder channelread bytetomessagedecoder java at io netty channel combinedchannelduplexhandler channelread combinedchannelduplexhandler java at io netty channel abstractchannelhandlercontext invokechannelread abstractchannelhandlercontext java at io netty channel abstractchannelhandlercontext invokechannelread abstractchannelhandlercontext java at io netty channel abstractchannelhandlercontext firechannelread abstractchannelhandlercontext java at io netty channel defaultchannelpipeline headcontext channelread defaultchannelpipeline java at io netty channel abstractchannelhandlercontext invokechannelread abstractchannelhandlercontext java at io netty channel abstractchannelhandlercontext invokechannelread abstractchannelhandlercontext java at io netty channel defaultchannelpipeline firechannelread defaultchannelpipeline java at io netty channel nio abstractniobytechannel niobyteunsafe read abstractniobytechannel java at io netty channel nio nioeventloop processselectedkey nioeventloop java at io netty channel nio nioeventloop processselectedkeysoptimized nioeventloop java at io netty channel nio nioeventloop processselectedkeys nioeventloop java at io netty channel nio nioeventloop run nioeventloop java at io netty util concurrent singlethreadeventexecutor run singlethreadeventexecutor java at io netty util internal threadexecutormap run threadexecutormap java at io netty util concurrent fastthreadlocalrunnable run fastthreadlocalrunnable java at java base java lang thread run thread java caused by javax ws rs internalservererrorexception http internal server error at org glassfish jersey client jerseyinvocation converttoexception jerseyinvocation java at org glassfish jersey client jerseyinvocation access jerseyinvocation java more | 0 |
158,793 | 13,747,945,662 | IssuesEvent | 2020-10-06 08:23:04 | nearform/mira | https://api.github.com/repos/nearform/mira | closed | Change relationship with samples in Quick Start Guide | documentation | **Is your feature request related to a problem? Please describe.**
The Mira samples are very different to each other and the instructions in `Clone and Initialise` can't be made suitably generic to cover all cases. This means that you have two sources of info that differ for getting started.
**Describe the solution you'd like**
The Quick Start Guide should have sections for:
* `Getting Started with a Sample` - this should explain why you would do that and then just link to the Sample Applications page
* `Getting Started with a New Application` - this should replace the `Clone and Initialise` section and be closer to the `Mira in Minutes` article, but without the S3 web hosting part.
**Describe alternatives you've considered**
Sticking with what we have :-(
| 1.0 | Change relationship with samples in Quick Start Guide - **Is your feature request related to a problem? Please describe.**
The Mira samples are very different to each other and the instructions in `Clone and Initialise` can't be made suitably generic to cover all cases. This means that you have two sources of info that differ for getting started.
**Describe the solution you'd like**
The Quick Start Guide should have sections for:
* `Getting Started with a Sample` - this should explain why you would do that and then just link to the Sample Applications page
* `Getting Started with a New Application` - this should replace the `Clone and Initialise` section and be closer to the `Mira in Minutes` article, but without the S3 web hosting part.
**Describe alternatives you've considered**
Sticking with what we have :-(
| non_priority | change relationship with samples in quick start guide is your feature request related to a problem please describe the mira samples are very different to each other and the instructions in clone and initialise can t be made suitably generic to cover all cases this means that you have two sources of info that differ for getting started describe the solution you d like the quick start guide should have sections for getting started with a sample this should explain why you would do that and then just link to the sample applications page getting started with a new application this should replace the clone and initialise section and be closer to the mira in minutes article but without the web hosting part describe alternatives you ve considered sticking with what we have | 0 |
214,630 | 24,077,748,290 | IssuesEvent | 2022-09-19 01:07:16 | renfei/SpringCloudDemo | https://api.github.com/repos/renfei/SpringCloudDemo | opened | CVE-2022-40150 (Medium) detected in jettison-1.3.7.jar | security vulnerability | ## CVE-2022-40150 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jettison-1.3.7.jar</b></p></summary>
<p>A StAX implementation for JSON.</p>
<p>Path to dependency file: /gateway/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/home/wss-scanner/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/home/wss-scanner/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/home/wss-scanner/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/home/wss-scanner/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/home/wss-scanner/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar</p>
<p>
Dependency Hierarchy:
- spring-cloud-starter-netflix-eureka-client-2.2.1.RELEASE.jar (Root Library)
- eureka-client-1.9.13.jar
- :x: **jettison-1.3.7.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/renfei/SpringCloudDemo/commit/3e0d29d6560c91c0b0e70b612a1bc5c66f0758cb">3e0d29d6560c91c0b0e70b612a1bc5c66f0758cb</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Those using Jettison to parse untrusted XML or JSON data may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by Out of memory. This effect may support a denial of service attack.
<p>Publish Date: 2022-09-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-40150>CVE-2022-40150</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-40150 (Medium) detected in jettison-1.3.7.jar - ## CVE-2022-40150 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jettison-1.3.7.jar</b></p></summary>
<p>A StAX implementation for JSON.</p>
<p>Path to dependency file: /gateway/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/home/wss-scanner/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/home/wss-scanner/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/home/wss-scanner/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/home/wss-scanner/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/home/wss-scanner/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar</p>
<p>
Dependency Hierarchy:
- spring-cloud-starter-netflix-eureka-client-2.2.1.RELEASE.jar (Root Library)
- eureka-client-1.9.13.jar
- :x: **jettison-1.3.7.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/renfei/SpringCloudDemo/commit/3e0d29d6560c91c0b0e70b612a1bc5c66f0758cb">3e0d29d6560c91c0b0e70b612a1bc5c66f0758cb</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Those using Jettison to parse untrusted XML or JSON data may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by Out of memory. This effect may support a denial of service attack.
<p>Publish Date: 2022-09-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-40150>CVE-2022-40150</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in jettison jar cve medium severity vulnerability vulnerable library jettison jar a stax implementation for json path to dependency file gateway pom xml path to vulnerable library home wss scanner repository org codehaus jettison jettison jettison jar home wss scanner repository org codehaus jettison jettison jettison jar home wss scanner repository org codehaus jettison jettison jettison jar home wss scanner repository org codehaus jettison jettison jettison jar home wss scanner repository org codehaus jettison jettison jettison jar home wss scanner repository org codehaus jettison jettison jettison jar dependency hierarchy spring cloud starter netflix eureka client release jar root library eureka client jar x jettison jar vulnerable library found in head commit a href found in base branch master vulnerability details those using jettison to parse untrusted xml or json data may be vulnerable to denial of service attacks dos if the parser is running on user supplied input an attacker may supply content that causes the parser to crash by out of memory this effect may support a denial of service attack publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href step up your open source security game with mend | 0 |
170,744 | 20,883,945,578 | IssuesEvent | 2022-03-23 01:30:29 | andythinkpower/vuex | https://api.github.com/repos/andythinkpower/vuex | opened | CVE-2021-33502 (High) detected in normalize-url-1.9.1.tgz | security vulnerability | ## CVE-2021-33502 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>normalize-url-1.9.1.tgz</b></p></summary>
<p>Normalize a URL</p>
<p>Library home page: <a href="https://registry.npmjs.org/normalize-url/-/normalize-url-1.9.1.tgz">https://registry.npmjs.org/normalize-url/-/normalize-url-1.9.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/normalize-url/package.json</p>
<p>
Dependency Hierarchy:
- css-loader-0.28.11.tgz (Root Library)
- cssnano-3.10.0.tgz
- postcss-normalize-url-3.0.8.tgz
- :x: **normalize-url-1.9.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>dev</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The normalize-url package before 4.5.1, 5.x before 5.3.1, and 6.x before 6.0.1 for Node.js has a ReDoS (regular expression denial of service) issue because it has exponential performance for data: URLs.
<p>Publish Date: 2021-05-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33502>CVE-2021-33502</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33502">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33502</a></p>
<p>Release Date: 2021-05-24</p>
<p>Fix Resolution (normalize-url): 4.5.1</p>
<p>Direct dependency fix Resolution (css-loader): 1.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-33502 (High) detected in normalize-url-1.9.1.tgz - ## CVE-2021-33502 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>normalize-url-1.9.1.tgz</b></p></summary>
<p>Normalize a URL</p>
<p>Library home page: <a href="https://registry.npmjs.org/normalize-url/-/normalize-url-1.9.1.tgz">https://registry.npmjs.org/normalize-url/-/normalize-url-1.9.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/normalize-url/package.json</p>
<p>
Dependency Hierarchy:
- css-loader-0.28.11.tgz (Root Library)
- cssnano-3.10.0.tgz
- postcss-normalize-url-3.0.8.tgz
- :x: **normalize-url-1.9.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>dev</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The normalize-url package before 4.5.1, 5.x before 5.3.1, and 6.x before 6.0.1 for Node.js has a ReDoS (regular expression denial of service) issue because it has exponential performance for data: URLs.
<p>Publish Date: 2021-05-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33502>CVE-2021-33502</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33502">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33502</a></p>
<p>Release Date: 2021-05-24</p>
<p>Fix Resolution (normalize-url): 4.5.1</p>
<p>Direct dependency fix Resolution (css-loader): 1.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in normalize url tgz cve high severity vulnerability vulnerable library normalize url tgz normalize a url library home page a href path to dependency file package json path to vulnerable library node modules normalize url package json dependency hierarchy css loader tgz root library cssnano tgz postcss normalize url tgz x normalize url tgz vulnerable library found in base branch dev vulnerability details the normalize url package before x before and x before for node js has a redos regular expression denial of service issue because it has exponential performance for data urls publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution normalize url direct dependency fix resolution css loader step up your open source security game with whitesource | 0 |
33,198 | 7,050,978,166 | IssuesEvent | 2018-01-03 09:37:53 | contao/core-bundle | https://api.github.com/repos/contao/core-bundle | opened | Set the locale in the front end | defect | As briefly discussed [here](https://github.com/contao/core-bundle/pull/1266#discussion_r159377615), we are currently not initializing the translator with the front end locale (page language). Also, we are only setting the `_locale` request attribute and not `Request::setLocale()`, which we should probably do as well.
| 1.0 | Set the locale in the front end - As briefly discussed [here](https://github.com/contao/core-bundle/pull/1266#discussion_r159377615), we are currently not initializing the translator with the front end locale (page language). Also, we are only setting the `_locale` request attribute and not `Request::setLocale()`, which we should probably do as well.
| non_priority | set the locale in the front end as briefly discussed we are currently not initializing the translator with the front end locale page language also we are only setting the locale request attribute and not request setlocale which we should probably do as well | 0 |
247,805 | 26,733,835,984 | IssuesEvent | 2023-01-30 07:51:19 | opfab/operatorfabric-core | https://api.github.com/repos/opfab/operatorfabric-core | closed | CVE-2022-42003 (High) detected in jackson-databind-2.13.3.jar - autoclosed | security vulnerability | ## CVE-2022-42003 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.13.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /src/test/api/karate/karateTests.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.13.3/56deb9ea2c93a7a556b3afbedd616d342963464e/jackson-databind-2.13.3.jar</p>
<p>
Dependency Hierarchy:
- karate-junit5-1.3.1.jar (Root Library)
- karate-core-1.3.1.jar
- armeria-1.18.0.jar
- :x: **jackson-databind-2.13.3.jar** (Vulnerable Library)
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In FasterXML jackson-databind before 2.14.0-rc1, resource exhaustion can occur because of a lack of a check in primitive value deserializers to avoid deep wrapper array nesting, when the UNWRAP_SINGLE_VALUE_ARRAYS feature is enabled. Additional fix version in 2.13.4.1 and 2.12.17.1
<p>Publish Date: 2022-10-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-42003>CVE-2022-42003</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.12.7.1,2.13.4.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-42003 (High) detected in jackson-databind-2.13.3.jar - autoclosed - ## CVE-2022-42003 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.13.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /src/test/api/karate/karateTests.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.13.3/56deb9ea2c93a7a556b3afbedd616d342963464e/jackson-databind-2.13.3.jar</p>
<p>
Dependency Hierarchy:
- karate-junit5-1.3.1.jar (Root Library)
- karate-core-1.3.1.jar
- armeria-1.18.0.jar
- :x: **jackson-databind-2.13.3.jar** (Vulnerable Library)
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In FasterXML jackson-databind before 2.14.0-rc1, resource exhaustion can occur because of a lack of a check in primitive value deserializers to avoid deep wrapper array nesting, when the UNWRAP_SINGLE_VALUE_ARRAYS feature is enabled. Additional fix version in 2.13.4.1 and 2.12.17.1
<p>Publish Date: 2022-10-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-42003>CVE-2022-42003</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.12.7.1,2.13.4.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar autoclosed cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file src test api karate karatetests gradle path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy karate jar root library karate core jar armeria jar x jackson databind jar vulnerable library found in base branch develop vulnerability details in fasterxml jackson databind before resource exhaustion can occur because of a lack of a check in primitive value deserializers to avoid deep wrapper array nesting when the unwrap single value arrays feature is enabled additional fix version in and publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with mend | 0 |
13,745 | 3,771,431,483 | IssuesEvent | 2016-03-16 17:34:31 | Azure/azure-iot-sdks | https://api.github.com/repos/Azure/azure-iot-sdks | closed | Intel Edison Documentation Error | documentation | Under the "Downloading the Azure IoT SDK to your Intel Edison" section of the [Intel Edison documentation](https://github.com/Azure/azure-iot-sdks/blob/master/doc/get_started/yocto-intel-edison-c.md#downloading-the-azure-iot-sdk-to-your-intel-edison), the following line:
```
git clone --recursive https://github.com/Azure/azure-iot-suite-sdks.git
```
Should be:
```
git clone --recursive https://github.com/Azure/azure-iot-sdks.git
``` | 1.0 | Intel Edison Documentation Error - Under the "Downloading the Azure IoT SDK to your Intel Edison" section of the [Intel Edison documentation](https://github.com/Azure/azure-iot-sdks/blob/master/doc/get_started/yocto-intel-edison-c.md#downloading-the-azure-iot-sdk-to-your-intel-edison), the following line:
```
git clone --recursive https://github.com/Azure/azure-iot-suite-sdks.git
```
Should be:
```
git clone --recursive https://github.com/Azure/azure-iot-sdks.git
``` | non_priority | intel edison documentation error under the downloading the azure iot sdk to your intel edison section of the the following line git clone recursive should be git clone recursive | 0 |
157,563 | 19,959,067,201 | IssuesEvent | 2022-01-28 05:23:32 | JeffResc/Is.gd-Node.js | https://api.github.com/repos/JeffResc/Is.gd-Node.js | closed | WS-2020-0163 (Medium) detected in marked-0.3.19.js, marked-0.3.19.tgz | security vulnerability | ## WS-2020-0163 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>marked-0.3.19.js</b>, <b>marked-0.3.19.tgz</b></p></summary>
<p>
<details><summary><b>marked-0.3.19.js</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/marked/0.3.19/marked.js">https://cdnjs.cloudflare.com/ajax/libs/marked/0.3.19/marked.js</a></p>
<p>Path to dependency file: Is.gd-Node.js/node_modules/marked/www/demo.html</p>
<p>Path to vulnerable library: Is.gd-Node.js/node_modules/marked/www/../lib/marked.js</p>
<p>
Dependency Hierarchy:
- :x: **marked-0.3.19.js** (Vulnerable Library)
</details>
<details><summary><b>marked-0.3.19.tgz</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://registry.npmjs.org/marked/-/marked-0.3.19.tgz">https://registry.npmjs.org/marked/-/marked-0.3.19.tgz</a></p>
<p>Path to dependency file: Is.gd-Node.js/package.json</p>
<p>Path to vulnerable library: Is.gd-Node.js/node_modules/marked/package.json</p>
<p>
Dependency Hierarchy:
- gulp-markdown-1.0.0.tgz (Root Library)
- :x: **marked-0.3.19.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/JeffResc/Is.gd-Node.js/commit/1036303aa40701aa25caa367da28c1e4e15926e3">1036303aa40701aa25caa367da28c1e4e15926e3</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
marked before 1.1.1 is vulnerable to Regular Expression Denial of Service (REDoS). rules.js have multiple unused capture groups which can lead to a Denial of Service.
<p>Publish Date: 2020-07-02
<p>URL: <a href=https://github.com/markedjs/marked/commit/bd4f8c464befad2b304d51e33e89e567326e62e0>WS-2020-0163</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/markedjs/marked/releases/tag/v1.1.1">https://github.com/markedjs/marked/releases/tag/v1.1.1</a></p>
<p>Release Date: 2020-07-02</p>
<p>Fix Resolution: marked - 1.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2020-0163 (Medium) detected in marked-0.3.19.js, marked-0.3.19.tgz - ## WS-2020-0163 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>marked-0.3.19.js</b>, <b>marked-0.3.19.tgz</b></p></summary>
<p>
<details><summary><b>marked-0.3.19.js</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/marked/0.3.19/marked.js">https://cdnjs.cloudflare.com/ajax/libs/marked/0.3.19/marked.js</a></p>
<p>Path to dependency file: Is.gd-Node.js/node_modules/marked/www/demo.html</p>
<p>Path to vulnerable library: Is.gd-Node.js/node_modules/marked/www/../lib/marked.js</p>
<p>
Dependency Hierarchy:
- :x: **marked-0.3.19.js** (Vulnerable Library)
</details>
<details><summary><b>marked-0.3.19.tgz</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://registry.npmjs.org/marked/-/marked-0.3.19.tgz">https://registry.npmjs.org/marked/-/marked-0.3.19.tgz</a></p>
<p>Path to dependency file: Is.gd-Node.js/package.json</p>
<p>Path to vulnerable library: Is.gd-Node.js/node_modules/marked/package.json</p>
<p>
Dependency Hierarchy:
- gulp-markdown-1.0.0.tgz (Root Library)
- :x: **marked-0.3.19.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/JeffResc/Is.gd-Node.js/commit/1036303aa40701aa25caa367da28c1e4e15926e3">1036303aa40701aa25caa367da28c1e4e15926e3</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
marked before 1.1.1 is vulnerable to Regular Expression Denial of Service (REDoS). rules.js have multiple unused capture groups which can lead to a Denial of Service.
<p>Publish Date: 2020-07-02
<p>URL: <a href=https://github.com/markedjs/marked/commit/bd4f8c464befad2b304d51e33e89e567326e62e0>WS-2020-0163</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/markedjs/marked/releases/tag/v1.1.1">https://github.com/markedjs/marked/releases/tag/v1.1.1</a></p>
<p>Release Date: 2020-07-02</p>
<p>Fix Resolution: marked - 1.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in marked js marked tgz ws medium severity vulnerability vulnerable libraries marked js marked tgz marked js a markdown parser built for speed library home page a href path to dependency file is gd node js node modules marked www demo html path to vulnerable library is gd node js node modules marked www lib marked js dependency hierarchy x marked js vulnerable library marked tgz a markdown parser built for speed library home page a href path to dependency file is gd node js package json path to vulnerable library is gd node js node modules marked package json dependency hierarchy gulp markdown tgz root library x marked tgz vulnerable library found in head commit a href found in base branch master vulnerability details marked before is vulnerable to regular expression denial of service redos rules js have multiple unused capture groups which can lead to a denial of service publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution marked step up your open source security game with whitesource | 0 |
111,914 | 17,048,561,386 | IssuesEvent | 2021-07-06 05:28:59 | vishalgoyal16444/mslearn-tailspin-spacegame-web | https://api.github.com/repos/vishalgoyal16444/mslearn-tailspin-spacegame-web | opened | CVE-2018-20821 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2018-20821 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass3.5.5</b>, <b>node-sass3.5.5</b>, <b>node-sass-4.14.1.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz</a></p>
<p>Path to dependency file: mslearn-tailspin-spacegame-web/package.json</p>
<p>Path to vulnerable library: mslearn-tailspin-spacegame-web/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.14.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/vishalgoyal16444/mslearn-tailspin-spacegame-web/commit/9dc0cb3749919e1417005d8857fa536e6b1e0d2f">9dc0cb3749919e1417005d8857fa536e6b1e0d2f</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The parsing component in LibSass through 3.5.5 allows attackers to cause a denial-of-service (uncontrolled recursion in Sass::Parser::parse_css_variable_value in parser.cpp).
<p>Publish Date: 2019-04-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20821>CVE-2018-20821</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20821">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20821</a></p>
<p>Release Date: 2019-04-23</p>
<p>Fix Resolution: LibSass - 3.6.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-20821 (Medium) detected in multiple libraries - ## CVE-2018-20821 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass3.5.5</b>, <b>node-sass3.5.5</b>, <b>node-sass-4.14.1.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz</a></p>
<p>Path to dependency file: mslearn-tailspin-spacegame-web/package.json</p>
<p>Path to vulnerable library: mslearn-tailspin-spacegame-web/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.14.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/vishalgoyal16444/mslearn-tailspin-spacegame-web/commit/9dc0cb3749919e1417005d8857fa536e6b1e0d2f">9dc0cb3749919e1417005d8857fa536e6b1e0d2f</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The parsing component in LibSass through 3.5.5 allows attackers to cause a denial-of-service (uncontrolled recursion in Sass::Parser::parse_css_variable_value in parser.cpp).
<p>Publish Date: 2019-04-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20821>CVE-2018-20821</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20821">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20821</a></p>
<p>Release Date: 2019-04-23</p>
<p>Fix Resolution: LibSass - 3.6.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries node node node sass tgz node sass tgz wrapper around libsass library home page a href path to dependency file mslearn tailspin spacegame web package json path to vulnerable library mslearn tailspin spacegame web node modules node sass package json dependency hierarchy x node sass tgz vulnerable library found in head commit a href found in base branch master vulnerability details the parsing component in libsass through allows attackers to cause a denial of service uncontrolled recursion in sass parser parse css variable value in parser cpp publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution libsass step up your open source security game with whitesource | 0 |
23,855 | 10,958,022,700 | IssuesEvent | 2019-11-27 08:30:39 | abder101/Security-Grade | https://api.github.com/repos/abder101/Security-Grade | closed | Exploit logs and detection tools | Intermediate Security VA.09 | Analyse logs and detection tools event to detect malicious patterns and automate notification for potential threats. | True | Exploit logs and detection tools - Analyse logs and detection tools event to detect malicious patterns and automate notification for potential threats. | non_priority | exploit logs and detection tools analyse logs and detection tools event to detect malicious patterns and automate notification for potential threats | 0 |
69,199 | 13,219,280,758 | IssuesEvent | 2020-08-17 10:11:45 | pwstrick/daily | https://api.github.com/repos/pwstrick/daily | opened | 二叉树的最近公共祖先 | Leetcode | [236. 二叉树的最近公共祖先](https://leetcode-cn.com/problems/lowest-common-ancestor-of-a-binary-tree/)
```javascript
/**
* Definition for a binary tree node.
* function TreeNode(val) {
* this.val = val;
* this.left = this.right = null;
* }
*/
/**
* @param {TreeNode} root
* @param {TreeNode} p
* @param {TreeNode} q
* @return {TreeNode}
*/
var lowestCommonAncestor = function(root, p, q) {
if(!root || root == p || root == q)
return root;
let left = lowestCommonAncestor(root.left, p, q); //p或q存在于左子树
let right = lowestCommonAncestor(root.right, p, q); //p或q存在于右子树
/**
* left为null,说明p和q在右子树中
* right为null,说明p和q在右子树中
* left和right都不为null,说明p和q分别存在于左右子树中
*/
return left == null ? right : (right == null ? left : root);
}
``` | 1.0 | 二叉树的最近公共祖先 - [236. 二叉树的最近公共祖先](https://leetcode-cn.com/problems/lowest-common-ancestor-of-a-binary-tree/)
```javascript
/**
* Definition for a binary tree node.
* function TreeNode(val) {
* this.val = val;
* this.left = this.right = null;
* }
*/
/**
* @param {TreeNode} root
* @param {TreeNode} p
* @param {TreeNode} q
* @return {TreeNode}
*/
var lowestCommonAncestor = function(root, p, q) {
if(!root || root == p || root == q)
return root;
let left = lowestCommonAncestor(root.left, p, q); //p或q存在于左子树
let right = lowestCommonAncestor(root.right, p, q); //p或q存在于右子树
/**
* left为null,说明p和q在右子树中
* right为null,说明p和q在右子树中
* left和right都不为null,说明p和q分别存在于左右子树中
*/
return left == null ? right : (right == null ? left : root);
}
``` | non_priority | 二叉树的最近公共祖先 javascript definition for a binary tree node function treenode val this val val this left this right null param treenode root param treenode p param treenode q return treenode var lowestcommonancestor function root p q if root root p root q return root let left lowestcommonancestor root left p q p或q存在于左子树 let right lowestcommonancestor root right p q p或q存在于右子树 left为null,说明p和q在右子树中 right为null,说明p和q在右子树中 left和right都不为null,说明p和q分别存在于左右子树中 return left null right right null left root | 0 |
86,961 | 15,755,910,365 | IssuesEvent | 2021-03-31 02:35:53 | turkdevops/node | https://api.github.com/repos/turkdevops/node | opened | CVE-2015-8851 (High) detected in node-uuid-1.4.1.tgz | security vulnerability | ## CVE-2015-8851 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-uuid-1.4.1.tgz</b></p></summary>
<p>Rigorous implementation of RFC4122 (v1 and v4) UUIDs.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-uuid/-/node-uuid-1.4.1.tgz">https://registry.npmjs.org/node-uuid/-/node-uuid-1.4.1.tgz</a></p>
<p>Path to dependency file: node/deps/npm/package.json</p>
<p>Path to vulnerable library: node/deps/npm/node_modules/request/node_modules/node-uuid/package.json</p>
<p>
Dependency Hierarchy:
- request-2.42.0.tgz (Root Library)
- :x: **node-uuid-1.4.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>archived-io.js-v0.10</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
node-uuid before 1.4.4 uses insufficiently random data to create a GUID, which could make it easier for attackers to have unspecified impact via brute force guessing.
<p>Publish Date: 2020-01-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-8851>CVE-2015-8851</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/93">https://nodesecurity.io/advisories/93</a></p>
<p>Release Date: 2020-01-30</p>
<p>Fix Resolution: 1.4.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2015-8851 (High) detected in node-uuid-1.4.1.tgz - ## CVE-2015-8851 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-uuid-1.4.1.tgz</b></p></summary>
<p>Rigorous implementation of RFC4122 (v1 and v4) UUIDs.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-uuid/-/node-uuid-1.4.1.tgz">https://registry.npmjs.org/node-uuid/-/node-uuid-1.4.1.tgz</a></p>
<p>Path to dependency file: node/deps/npm/package.json</p>
<p>Path to vulnerable library: node/deps/npm/node_modules/request/node_modules/node-uuid/package.json</p>
<p>
Dependency Hierarchy:
- request-2.42.0.tgz (Root Library)
- :x: **node-uuid-1.4.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>archived-io.js-v0.10</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
node-uuid before 1.4.4 uses insufficiently random data to create a GUID, which could make it easier for attackers to have unspecified impact via brute force guessing.
<p>Publish Date: 2020-01-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-8851>CVE-2015-8851</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/93">https://nodesecurity.io/advisories/93</a></p>
<p>Release Date: 2020-01-30</p>
<p>Fix Resolution: 1.4.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in node uuid tgz cve high severity vulnerability vulnerable library node uuid tgz rigorous implementation of and uuids library home page a href path to dependency file node deps npm package json path to vulnerable library node deps npm node modules request node modules node uuid package json dependency hierarchy request tgz root library x node uuid tgz vulnerable library found in base branch archived io js vulnerability details node uuid before uses insufficiently random data to create a guid which could make it easier for attackers to have unspecified impact via brute force guessing publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
23,916 | 16,687,336,642 | IssuesEvent | 2021-06-08 09:22:28 | SciTools/cf-units | https://api.github.com/repos/SciTools/cf-units | opened | Reboot cf-units | Type: Infrastructure | To-do checklist:
- [ ] Enable GH discussions
- [ ] Create Releases GH discussions category
- [ ] Create `3.0` release discussion
- [ ] Add Issue templates
- [ ] Add PR template
- [ ] Create `3.0` release milestone
- [ ] Create `3.0` project board
- [ ] Update labels
- [ ] Configure repo settings
- [ ] Allow squash merging only
- [ ] Require conversation resolution before merging
- [ ] Require linear history
- [ ] Migrate CI from `travis-ci` to `cirrus-ci`
- [ ] Adopt `setuptools-scm` and drop `versioneer`
- [ ] Adopt `pre-commit`
- [ ] `black`
- [ ] `flake8`
- [ ] `isort`
- [ ] Migrate `setup.py` to `setup.cfg`
- [ ] Rationalise package dependencies for `conda` and PyPI
- [ ] Update `README.md` badges
- [ ] Remove `six` dependency | 1.0 | Reboot cf-units - To-do checklist:
- [ ] Enable GH discussions
- [ ] Create Releases GH discussions category
- [ ] Create `3.0` release discussion
- [ ] Add Issue templates
- [ ] Add PR template
- [ ] Create `3.0` release milestone
- [ ] Create `3.0` project board
- [ ] Update labels
- [ ] Configure repo settings
- [ ] Allow squash merging only
- [ ] Require conversation resolution before merging
- [ ] Require linear history
- [ ] Migrate CI from `travis-ci` to `cirrus-ci`
- [ ] Adopt `setuptools-scm` and drop `versioneer`
- [ ] Adopt `pre-commit`
- [ ] `black`
- [ ] `flake8`
- [ ] `isort`
- [ ] Migrate `setup.py` to `setup.cfg`
- [ ] Rationalise package dependencies for `conda` and PyPI
- [ ] Update `README.md` badges
- [ ] Remove `six` dependency | non_priority | reboot cf units to do checklist enable gh discussions create releases gh discussions category create release discussion add issue templates add pr template create release milestone create project board update labels configure repo settings allow squash merging only require conversation resolution before merging require linear history migrate ci from travis ci to cirrus ci adopt setuptools scm and drop versioneer adopt pre commit black isort migrate setup py to setup cfg rationalise package dependencies for conda and pypi update readme md badges remove six dependency | 0 |
221,257 | 24,601,187,564 | IssuesEvent | 2022-10-14 12:39:11 | LynRodWS/alcor | https://api.github.com/repos/LynRodWS/alcor | opened | CVE-2022-42889 (Medium) detected in commons-text-1.6.jar | security vulnerability | ## CVE-2022-42889 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-text-1.6.jar</b></p></summary>
<p>Apache Commons Text is a library focused on algorithms working on strings.</p>
<p>Library home page: <a href="http://commons.apache.org/proper/commons-text">http://commons.apache.org/proper/commons-text</a></p>
<p>Path to dependency file: /services/api_gateway/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/commons/commons-text/1.6/commons-text-1.6.jar</p>
<p>
Dependency Hierarchy:
- spring-cloud-starter-contract-stub-runner-2.1.2.RELEASE.jar (Root Library)
- spring-cloud-contract-stub-runner-2.1.2.RELEASE.jar
- spring-cloud-contract-spec-2.1.2.RELEASE.jar
- :x: **commons-text-1.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/LynRodWS/alcor/commit/3c4e28556738e020da91fd03c3aaa5d9a7c1cfed">3c4e28556738e020da91fd03c3aaa5d9a7c1cfed</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache Commons Text performs variable interpolation, allowing properties to be dynamically evaluated and expanded. The standard format for interpolation is "${prefix:name}", where "prefix" is used to locate an instance of org.apache.commons.text.lookup.StringLookup that performs the interpolation. Starting with version 1.5 and continuing through 1.9, the set of default Lookup instances included interpolators that could result in arbitrary code execution or contact with remote servers. These lookups are: - "script" - execute expressions using the JVM script execution engine (javax.script) - "dns" - resolve dns records - "url" - load values from urls, including from remote servers Applications using the interpolation defaults in the affected versions may be vulnerable to remote code execution or unintentional contact with remote servers if untrusted configuration values are used. Users are recommended to upgrade to Apache Commons Text 1.10.0, which disables the problematic interpolators by default.
<p>Publish Date: 2022-10-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-42889>CVE-2022-42889</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.openwall.com/lists/oss-security/2022/10/13/4">https://www.openwall.com/lists/oss-security/2022/10/13/4</a></p>
<p>Release Date: 2022-10-13</p>
<p>Fix Resolution (org.apache.commons:commons-text): 1.10.0</p>
<p>Direct dependency fix Resolution (org.springframework.cloud:spring-cloud-starter-contract-stub-runner): 3.0.6</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| True | CVE-2022-42889 (Medium) detected in commons-text-1.6.jar - ## CVE-2022-42889 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-text-1.6.jar</b></p></summary>
<p>Apache Commons Text is a library focused on algorithms working on strings.</p>
<p>Library home page: <a href="http://commons.apache.org/proper/commons-text">http://commons.apache.org/proper/commons-text</a></p>
<p>Path to dependency file: /services/api_gateway/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/commons/commons-text/1.6/commons-text-1.6.jar</p>
<p>
Dependency Hierarchy:
- spring-cloud-starter-contract-stub-runner-2.1.2.RELEASE.jar (Root Library)
- spring-cloud-contract-stub-runner-2.1.2.RELEASE.jar
- spring-cloud-contract-spec-2.1.2.RELEASE.jar
- :x: **commons-text-1.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/LynRodWS/alcor/commit/3c4e28556738e020da91fd03c3aaa5d9a7c1cfed">3c4e28556738e020da91fd03c3aaa5d9a7c1cfed</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache Commons Text performs variable interpolation, allowing properties to be dynamically evaluated and expanded. The standard format for interpolation is "${prefix:name}", where "prefix" is used to locate an instance of org.apache.commons.text.lookup.StringLookup that performs the interpolation. Starting with version 1.5 and continuing through 1.9, the set of default Lookup instances included interpolators that could result in arbitrary code execution or contact with remote servers. These lookups are: - "script" - execute expressions using the JVM script execution engine (javax.script) - "dns" - resolve dns records - "url" - load values from urls, including from remote servers Applications using the interpolation defaults in the affected versions may be vulnerable to remote code execution or unintentional contact with remote servers if untrusted configuration values are used. Users are recommended to upgrade to Apache Commons Text 1.10.0, which disables the problematic interpolators by default.
<p>Publish Date: 2022-10-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-42889>CVE-2022-42889</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.openwall.com/lists/oss-security/2022/10/13/4">https://www.openwall.com/lists/oss-security/2022/10/13/4</a></p>
<p>Release Date: 2022-10-13</p>
<p>Fix Resolution (org.apache.commons:commons-text): 1.10.0</p>
<p>Direct dependency fix Resolution (org.springframework.cloud:spring-cloud-starter-contract-stub-runner): 3.0.6</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| non_priority | cve medium detected in commons text jar cve medium severity vulnerability vulnerable library commons text jar apache commons text is a library focused on algorithms working on strings library home page a href path to dependency file services api gateway pom xml path to vulnerable library home wss scanner repository org apache commons commons text commons text jar dependency hierarchy spring cloud starter contract stub runner release jar root library spring cloud contract stub runner release jar spring cloud contract spec release jar x commons text jar vulnerable library found in head commit a href found in base branch master vulnerability details apache commons text performs variable interpolation allowing properties to be dynamically evaluated and expanded the standard format for interpolation is prefix name where prefix is used to locate an instance of org apache commons text lookup stringlookup that performs the interpolation starting with version and continuing through the set of default lookup instances included interpolators that could result in arbitrary code execution or contact with remote servers these lookups are script execute expressions using the jvm script execution engine javax script dns resolve dns records url load values from urls including from remote servers applications using the interpolation defaults in the affected versions may be vulnerable to remote code execution or unintentional contact with remote servers if untrusted configuration values are used users are recommended to upgrade to apache commons text which disables the problematic interpolators by default publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache commons commons text direct dependency fix resolution org springframework cloud spring cloud starter contract stub runner check this box to open an automated fix pr | 0 |
10,817 | 2,967,676,071 | IssuesEvent | 2015-07-13 02:47:15 | ohnno/Brosa | https://api.github.com/repos/ohnno/Brosa | opened | Scroll To Top Behavior Tweak | design fix / tweak | Location: Global
I've seen the scroll to top button that appears after you scroll a certain distance clash with other elements on the screen. Can we move the trigger for it appearing further down the screen. I'm guessing (400-800px downward) would be about right. | 1.0 | Scroll To Top Behavior Tweak - Location: Global
I've seen the scroll to top button that appears after you scroll a certain distance clash with other elements on the screen. Can we move the trigger for it appearing further down the screen. I'm guessing (400-800px downward) would be about right. | non_priority | scroll to top behavior tweak location global i ve seen the scroll to top button that appears after you scroll a certain distance clash with other elements on the screen can we move the trigger for it appearing further down the screen i m guessing downward would be about right | 0 |
123,055 | 16,436,616,480 | IssuesEvent | 2021-05-20 09:56:58 | etsy/open-api | https://api.github.com/repos/etsy/open-api | opened | [ENDPOINT] Proposed design change for <GetShopReceipts> | API Design | **Current Endpoint Design**
The new v3 response does not match that of the v2, there are some missing elements.
**Proposed Endpoint Design Change**
* Shipping_details
* Returns a _receipt_shipping_id_ but there does not appear to be an endpoint to retrieve this data.
* Coupon (or some alternative)
* free_shipping
* fixed_discount
* pct_discount
* Listings
**Why are you proposing this change?**
* This will push more customers to hit their rate limits with extra api calls
* Even in the case of Shipping_details does not seem to be a way to retrieve the required data
* Functionality does not match existing functionality
| 1.0 | [ENDPOINT] Proposed design change for <GetShopReceipts> - **Current Endpoint Design**
The new v3 response does not match that of the v2, there are some missing elements.
**Proposed Endpoint Design Change**
* Shipping_details
* Returns a _receipt_shipping_id_ but there does not appear to be an endpoint to retrieve this data.
* Coupon (or some alternative)
* free_shipping
* fixed_discount
* pct_discount
* Listings
**Why are you proposing this change?**
* This will push more customers to hit their rate limits with extra api calls
* Even in the case of Shipping_details does not seem to be a way to retrieve the required data
* Functionality does not match existing functionality
| non_priority | proposed design change for current endpoint design the new response does not match that of the there are some missing elements proposed endpoint design change shipping details returns a receipt shipping id but there does not appear to be an endpoint to retrieve this data coupon or some alternative free shipping fixed discount pct discount listings why are you proposing this change this will push more customers to hit their rate limits with extra api calls even in the case of shipping details does not seem to be a way to retrieve the required data functionality does not match existing functionality | 0 |
29,269 | 11,739,388,693 | IssuesEvent | 2020-03-11 17:37:28 | heholek/dtale | https://api.github.com/repos/heholek/dtale | opened | CVE-2018-11499 (High) detected in multiple libraries | security vulnerability | ## CVE-2018-11499 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.13.0.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.13.0.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.13.0.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.13.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/dtale/package.json</p>
<p>Path to vulnerable library: /dtale/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.13.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/heholek/dtale/commit/c12bfd5f568d2005294b975eebb03ec5c56e95b2">c12bfd5f568d2005294b975eebb03ec5c56e95b2</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A use-after-free vulnerability exists in handle_error() in sass_context.cpp in LibSass 3.4.x and 3.5.x through 3.5.4 that could be leveraged to cause a denial of service (application crash) or possibly unspecified other impact.
<p>Publish Date: 2018-05-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-11499>CVE-2018-11499</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11499">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11499</a></p>
<p>Release Date: 2018-05-26</p>
<p>Fix Resolution: 3.6.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-11499 (High) detected in multiple libraries - ## CVE-2018-11499 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.13.0.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.13.0.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.13.0.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.13.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/dtale/package.json</p>
<p>Path to vulnerable library: /dtale/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.13.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/heholek/dtale/commit/c12bfd5f568d2005294b975eebb03ec5c56e95b2">c12bfd5f568d2005294b975eebb03ec5c56e95b2</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A use-after-free vulnerability exists in handle_error() in sass_context.cpp in LibSass 3.4.x and 3.5.x through 3.5.4 that could be leveraged to cause a denial of service (application crash) or possibly unspecified other impact.
<p>Publish Date: 2018-05-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-11499>CVE-2018-11499</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11499">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11499</a></p>
<p>Release Date: 2018-05-26</p>
<p>Fix Resolution: 3.6.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries node sass tgz node sass tgz wrapper around libsass library home page a href path to dependency file tmp ws scm dtale package json path to vulnerable library dtale node modules node sass package json dependency hierarchy x node sass tgz vulnerable library found in head commit a href vulnerability details a use after free vulnerability exists in handle error in sass context cpp in libsass x and x through that could be leveraged to cause a denial of service application crash or possibly unspecified other impact publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
310 | 3,040,460,446 | IssuesEvent | 2015-08-07 15:31:04 | palazzem/wheelie | https://api.github.com/repos/palazzem/wheelie | closed | Task#run() method should receive Wheelie global options | architecture/design | in this way, if it's required, you may:
```
// tasks/foo.js
// ...
function run(gulp, config, globals) {
return function() {
if (globals.production) {
// do something
} else {
// do something else
}
}
}
// ...
``` | 1.0 | Task#run() method should receive Wheelie global options - in this way, if it's required, you may:
```
// tasks/foo.js
// ...
function run(gulp, config, globals) {
return function() {
if (globals.production) {
// do something
} else {
// do something else
}
}
}
// ...
``` | non_priority | task run method should receive wheelie global options in this way if it s required you may tasks foo js function run gulp config globals return function if globals production do something else do something else | 0 |
44,808 | 11,505,100,607 | IssuesEvent | 2020-02-13 01:20:45 | openshift/origin | https://api.github.com/repos/openshift/origin | closed | Expose `OPENSHIFT_BUILD_*` parameters as Docker Build `ARG` values. | component/build lifecycle/rotten sig/developer-experience | ## Feature Suggestion
Expose `OPENSHIFT_BUILD_*` parameters as Docker Build `ARG` values.
Unless I am missing something (apologies if so) I cannot see a way for the Dockerfile to reference these values. Reading through `builder/common.go` and `builder/docker.go` it looks like the various `OPENSHIFT_BUILD_*` values are provided in string literal form and appended onto the Dockerfile to provide `ENV` values inside the container. They are not supplied as parameters which can be accessed using `ARG`.
## Version
```
oc v3.11.0+0cbc58b
kubernetes v1.11.0+d4cacc0
features: Basic-Auth SSPI Kerberos SPNEGO
Server https://<snip>
openshift v3.11.117
kubernetes v1.11.0+d4cacc0
```
## Use case
Our current build tool in Azure DevOps supplies the `BUILD_ID` as an `ARG` to the Dockerfile. During the image build, once the ID of the image is known, all static assets have this included in their file names. This serves two purposes:
1. Cache busting of static assets to ensure that release of a new image requires clients to use new static assets.
2. Avoids file name clashes and overwrites when static assets are migrated to a CDN during a rolling deploy when both images might still be serving traffic and both versions of static assets should remain addressable.
Current code stub to achieve this:
```
ARG BUILD_ID # Get value from DevOps
ENV BUILD_ID ${BUILD_ID:-B0000} # Safety line with default fallback
RUN sh startup-scripts/addHash.sh $BUILD_ID # Add hash value to static assets
```
## Possible Workaround
I suspect we could possibly do something similar using `buildArgs` under `dockerStrategy`. It requires an extra layer of work, but I think it would work... just I'm not currently aware of what variables I can access there that would be useful. Anything unique to the build is useful/workable, hence I was looking for any of `OPENSHIFT_BUILD_*`.
e.g.:
```
strategy:
dockerStrategy:
buildArgs:
name: BUILD_ID
value: ${SOME_VARIABLE_HERE}
``` | 1.0 | Expose `OPENSHIFT_BUILD_*` parameters as Docker Build `ARG` values. - ## Feature Suggestion
Expose `OPENSHIFT_BUILD_*` parameters as Docker Build `ARG` values.
Unless I am missing something (apologies if so) I cannot see a way for the Dockerfile to reference these values. Reading through `builder/common.go` and `builder/docker.go` it looks like the various `OPENSHIFT_BUILD_*` values are provided in string literal form and appended onto the Dockerfile to provide `ENV` values inside the container. They are not supplied as parameters which can be accessed using `ARG`.
## Version
```
oc v3.11.0+0cbc58b
kubernetes v1.11.0+d4cacc0
features: Basic-Auth SSPI Kerberos SPNEGO
Server https://<snip>
openshift v3.11.117
kubernetes v1.11.0+d4cacc0
```
## Use case
Our current build tool in Azure DevOps supplies the `BUILD_ID` as an `ARG` to the Dockerfile. During the image build, once the ID of the image is known, all static assets have this included in their file names. This serves two purposes:
1. Cache busting of static assets to ensure that release of a new image requires clients to use new static assets.
2. Avoids file name clashes and overwrites when static assets are migrated to a CDN during a rolling deploy when both images might still be serving traffic and both versions of static assets should remain addressable.
Current code stub to achieve this:
```
ARG BUILD_ID # Get value from DevOps
ENV BUILD_ID ${BUILD_ID:-B0000} # Safety line with default fallback
RUN sh startup-scripts/addHash.sh $BUILD_ID # Add hash value to static assets
```
## Possible Workaround
I suspect we could possibly do something similar using `buildArgs` under `dockerStrategy`. It requires an extra layer of work, but I think it would work... just I'm not currently aware of what variables I can access there that would be useful. Anything unique to the build is useful/workable, hence I was looking for any of `OPENSHIFT_BUILD_*`.
e.g.:
```
strategy:
dockerStrategy:
buildArgs:
name: BUILD_ID
value: ${SOME_VARIABLE_HERE}
``` | non_priority | expose openshift build parameters as docker build arg values feature suggestion expose openshift build parameters as docker build arg values unless i am missing something apologies if so i cannot see a way for the dockerfile to reference these values reading through builder common go and builder docker go it looks like the various openshift build values are provided in string literal form and appended onto the dockerfile to provide env values inside the container they are not supplied as parameters which can be accessed using arg version oc kubernetes features basic auth sspi kerberos spnego server openshift kubernetes use case our current build tool in azure devops supplies the build id as an arg to the dockerfile during the image build once the id of the image is known all static assets have this included in their file names this serves two purposes cache busting of static assets to ensure that release of a new image requires clients to use new static assets avoids file name clashes and overwrites when static assets are migrated to a cdn during a rolling deploy when both images might still be serving traffic and both versions of static assets should remain addressable current code stub to achieve this arg build id get value from devops env build id build id safety line with default fallback run sh startup scripts addhash sh build id add hash value to static assets possible workaround i suspect we could possibly do something similar using buildargs under dockerstrategy it requires an extra layer of work but i think it would work just i m not currently aware of what variables i can access there that would be useful anything unique to the build is useful workable hence i was looking for any of openshift build e g strategy dockerstrategy buildargs name build id value some variable here | 0 |
47,499 | 13,238,080,377 | IssuesEvent | 2020-08-18 23:16:23 | benchabot/expo | https://api.github.com/repos/benchabot/expo | opened | CVE-2019-10744 (High) detected in lodash-1.0.2.tgz, lodash-3.10.1.tgz | security vulnerability | ## CVE-2019-10744 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-1.0.2.tgz</b>, <b>lodash-3.10.1.tgz</b></p></summary>
<p>
<details><summary><b>lodash-1.0.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz">https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/expo/ios/versioned-react-native/ABI35_0_0/Libraries/Animated/release/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/expo/ios/versioned-react-native/ABI35_0_0/Libraries/Animated/release/node_modules/globule/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- gulp-3.9.1.tgz (Root Library)
- vinyl-fs-0.3.14.tgz
- glob-watcher-0.0.6.tgz
- gaze-0.5.2.tgz
- globule-0.1.0.tgz
- :x: **lodash-1.0.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-3.10.1.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz">https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/expo/ios/versioned-react-native/ABI35_0_0/Libraries/Animated/release/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/expo/ios/versioned-react-native/ABI35_0_0/Libraries/Animated/release/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- babel-core-5.8.38.tgz (Root Library)
- :x: **lodash-3.10.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/benchabot/expo/commit/cacc29b6e5c0194b7bb203c7f0f94ada84f9fcab">cacc29b6e5c0194b7bb203c7f0f94ada84f9fcab</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
<p>Publish Date: 2019-07-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10744>CVE-2019-10744</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/lodash/lodash/pull/4336/commits/a01e4fa727e7294cb7b2845570ba96b206926790">https://github.com/lodash/lodash/pull/4336/commits/a01e4fa727e7294cb7b2845570ba96b206926790</a></p>
<p>Release Date: 2019-07-08</p>
<p>Fix Resolution: 4.17.12</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-10744 (High) detected in lodash-1.0.2.tgz, lodash-3.10.1.tgz - ## CVE-2019-10744 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-1.0.2.tgz</b>, <b>lodash-3.10.1.tgz</b></p></summary>
<p>
<details><summary><b>lodash-1.0.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz">https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/expo/ios/versioned-react-native/ABI35_0_0/Libraries/Animated/release/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/expo/ios/versioned-react-native/ABI35_0_0/Libraries/Animated/release/node_modules/globule/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- gulp-3.9.1.tgz (Root Library)
- vinyl-fs-0.3.14.tgz
- glob-watcher-0.0.6.tgz
- gaze-0.5.2.tgz
- globule-0.1.0.tgz
- :x: **lodash-1.0.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-3.10.1.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz">https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/expo/ios/versioned-react-native/ABI35_0_0/Libraries/Animated/release/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/expo/ios/versioned-react-native/ABI35_0_0/Libraries/Animated/release/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- babel-core-5.8.38.tgz (Root Library)
- :x: **lodash-3.10.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/benchabot/expo/commit/cacc29b6e5c0194b7bb203c7f0f94ada84f9fcab">cacc29b6e5c0194b7bb203c7f0f94ada84f9fcab</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
<p>Publish Date: 2019-07-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10744>CVE-2019-10744</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/lodash/lodash/pull/4336/commits/a01e4fa727e7294cb7b2845570ba96b206926790">https://github.com/lodash/lodash/pull/4336/commits/a01e4fa727e7294cb7b2845570ba96b206926790</a></p>
<p>Release Date: 2019-07-08</p>
<p>Fix Resolution: 4.17.12</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in lodash tgz lodash tgz cve high severity vulnerability vulnerable libraries lodash tgz lodash tgz lodash tgz a utility library delivering consistency customization performance and extras library home page a href path to dependency file tmp ws scm expo ios versioned react native libraries animated release package json path to vulnerable library tmp ws scm expo ios versioned react native libraries animated release node modules globule node modules lodash package json dependency hierarchy gulp tgz root library vinyl fs tgz glob watcher tgz gaze tgz globule tgz x lodash tgz vulnerable library lodash tgz the modern build of lodash modular utilities library home page a href path to dependency file tmp ws scm expo ios versioned react native libraries animated release package json path to vulnerable library tmp ws scm expo ios versioned react native libraries animated release node modules lodash package json dependency hierarchy babel core tgz root library x lodash tgz vulnerable library found in head commit a href vulnerability details versions of lodash lower than are vulnerable to prototype pollution the function defaultsdeep could be tricked into adding or modifying properties of object prototype using a constructor payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
157,952 | 19,988,942,302 | IssuesEvent | 2022-01-31 02:06:38 | sureng-ws-ibm/sg-x-nodegoat | https://api.github.com/repos/sureng-ws-ibm/sg-x-nodegoat | closed | WS-2019-0425 (Medium) detected in mocha-2.5.3.tgz - autoclosed | security vulnerability | ## WS-2019-0425 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mocha-2.5.3.tgz</b></p></summary>
<p>simple, flexible, fun test framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/mocha/-/mocha-2.5.3.tgz">https://registry.npmjs.org/mocha/-/mocha-2.5.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mocha/package.json</p>
<p>
Dependency Hierarchy:
- :x: **mocha-2.5.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sureng-ws-ibm/sg-x-nodegoat/commit/81cd799c64e09f7670559bce715f20a9ec7821d5">81cd799c64e09f7670559bce715f20a9ec7821d5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Mocha is vulnerable to ReDoS attack. If the stack trace in utils.js begins with a large error message, and full-trace is not enabled, utils.stackTraceFilter() will take exponential run time.
<p>Publish Date: 2019-01-24
<p>URL: <a href=https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559>WS-2019-0425</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="v6.0.0">v6.0.0</a></p>
<p>Release Date: 2019-01-24</p>
<p>Fix Resolution: 6.0.0</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"mocha","packageVersion":"2.5.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"mocha:2.5.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"6.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"WS-2019-0425","vulnerabilityDetails":"Mocha is vulnerable to ReDoS attack. If the stack trace in utils.js begins with a large error message, and full-trace is not enabled, utils.stackTraceFilter() will take exponential run time.","vulnerabilityUrl":"https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | WS-2019-0425 (Medium) detected in mocha-2.5.3.tgz - autoclosed - ## WS-2019-0425 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mocha-2.5.3.tgz</b></p></summary>
<p>simple, flexible, fun test framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/mocha/-/mocha-2.5.3.tgz">https://registry.npmjs.org/mocha/-/mocha-2.5.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mocha/package.json</p>
<p>
Dependency Hierarchy:
- :x: **mocha-2.5.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sureng-ws-ibm/sg-x-nodegoat/commit/81cd799c64e09f7670559bce715f20a9ec7821d5">81cd799c64e09f7670559bce715f20a9ec7821d5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Mocha is vulnerable to ReDoS attack. If the stack trace in utils.js begins with a large error message, and full-trace is not enabled, utils.stackTraceFilter() will take exponential run time.
<p>Publish Date: 2019-01-24
<p>URL: <a href=https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559>WS-2019-0425</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="v6.0.0">v6.0.0</a></p>
<p>Release Date: 2019-01-24</p>
<p>Fix Resolution: 6.0.0</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"mocha","packageVersion":"2.5.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"mocha:2.5.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"6.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"WS-2019-0425","vulnerabilityDetails":"Mocha is vulnerable to ReDoS attack. If the stack trace in utils.js begins with a large error message, and full-trace is not enabled, utils.stackTraceFilter() will take exponential run time.","vulnerabilityUrl":"https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | ws medium detected in mocha tgz autoclosed ws medium severity vulnerability vulnerable library mocha tgz simple flexible fun test framework library home page a href path to dependency file package json path to vulnerable library node modules mocha package json dependency hierarchy x mocha tgz vulnerable library found in head commit a href found in base branch master vulnerability details mocha is vulnerable to redos attack if the stack trace in utils js begins with a large error message and full trace is not enabled utils stacktracefilter will take exponential run time publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin release date fix resolution rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree mocha isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails mocha is vulnerable to redos attack if the stack trace in utils js begins with a large error message and full trace is not enabled utils stacktracefilter will take exponential run time vulnerabilityurl | 0 |
72,814 | 19,513,887,500 | IssuesEvent | 2021-12-29 06:27:39 | CapsCollective/ozymandias | https://api.github.com/repos/CapsCollective/ozymandias | opened | Port to Nintendo Switch | builds | **Feature description**
<!-- A clear and concise description of what the feature should be -->
Develop and release a port for the Nintendo Switch console.
**Acceptance criteria/subtasks**
<!-- Remove this if none exist -->
- [ ] Get signed up with Nintendo
- [ ] Port it
**TODO**
<!-- Complete these once you have created the feature issue -->
- [x] Add the appropriate label for the feature (i.e. environment, user interface, game logic, etc.)
- [x] Add the feature to the "Development Board"
| 1.0 | Port to Nintendo Switch - **Feature description**
<!-- A clear and concise description of what the feature should be -->
Develop and release a port for the Nintendo Switch console.
**Acceptance criteria/subtasks**
<!-- Remove this if none exist -->
- [ ] Get signed up with Nintendo
- [ ] Port it
**TODO**
<!-- Complete these once you have created the feature issue -->
- [x] Add the appropriate label for the feature (i.e. environment, user interface, game logic, etc.)
- [x] Add the feature to the "Development Board"
| non_priority | port to nintendo switch feature description develop and release a port for the nintendo switch console acceptance criteria subtasks get signed up with nintendo port it todo add the appropriate label for the feature i e environment user interface game logic etc add the feature to the development board | 0 |
8,900 | 3,010,713,811 | IssuesEvent | 2015-07-28 14:33:39 | joe-bader/test-repo | https://api.github.com/repos/joe-bader/test-repo | opened | [CNVERG-37] IE11, IE10, Firefox: Space area: Full screen function doesn't work | Crossbrowser Testing QA | <b><i>[reporter="v.dementyev", created="Tue, 21 Jul 2015 13:17:57 +0300"]</i></b>
<ol>
<li>Log into the application</li>
<li>Open any space</li>
<li>Click the "full screen" icon</li>
</ol>
<p>Result: Nothing happens</p> | 1.0 | [CNVERG-37] IE11, IE10, Firefox: Space area: Full screen function doesn't work - <b><i>[reporter="v.dementyev", created="Tue, 21 Jul 2015 13:17:57 +0300"]</i></b>
<ol>
<li>Log into the application</li>
<li>Open any space</li>
<li>Click the "full screen" icon</li>
</ol>
<p>Result: Nothing happens</p> | non_priority | firefox space area full screen function doesn t work log into the application open any space click the full screen icon result nothing happens | 0 |
131,416 | 18,281,758,571 | IssuesEvent | 2021-10-05 04:58:32 | dotnet/aspnetcore | https://api.github.com/repos/dotnet/aspnetcore | closed | Namespace names are always grayed out in _ViewImports.cshtml | Needs: Design area-razor.tooling | Consider the following in a project's `_ViewImports.cshtml` file:
``` html
@using RazorPagesWebApplication
@using RazorPagesWebApplication.Data
@using Microsoft.AspNetCore.Identity
```
The actual namespaces are all grayed out by the editor suggesting they aren't needed. | 1.0 | Namespace names are always grayed out in _ViewImports.cshtml - Consider the following in a project's `_ViewImports.cshtml` file:
``` html
@using RazorPagesWebApplication
@using RazorPagesWebApplication.Data
@using Microsoft.AspNetCore.Identity
```
The actual namespaces are all grayed out by the editor suggesting they aren't needed. | non_priority | namespace names are always grayed out in viewimports cshtml consider the following in a project s viewimports cshtml file html using razorpageswebapplication using razorpageswebapplication data using microsoft aspnetcore identity the actual namespaces are all grayed out by the editor suggesting they aren t needed | 0 |
306,787 | 23,172,044,798 | IssuesEvent | 2022-07-30 21:45:15 | workbits-raio/desafio-1 | https://api.github.com/repos/workbits-raio/desafio-1 | closed | 000 - Example | documentation | Example
------------------------
- Let's control the Challenges as issues
- We can use it as things we want / we would create or work with.
- We can use it as a problem highlight or ask for help - let's do it as a group. | 1.0 | 000 - Example - Example
------------------------
- Let's control the Challenges as issues
- We can use it as things we want / we would create or work with.
- We can use it as a problem highlight or ask for help - let's do it as a group. | non_priority | example example let s control the challenges as issues we can use it as things we want we would create or work with we can use it as a problem highlight or ask for help let s do it as a group | 0 |
27,312 | 4,052,599,810 | IssuesEvent | 2016-05-24 03:45:11 | EmergingTechnologyAdvisors/node-serialport | https://api.github.com/repos/EmergingTechnologyAdvisors/node-serialport | closed | Cleanup flow control options during port construction | backlog design | We have [flags, an array, and a boolean](https://github.com/EmergingTechnologyAdvisors/node-serialport/blob/3.1.2/README.md#serialport-path-options-openimmediately-callback) to set the flow control flags on a port. Lets keep it just the flags.
This would be a breaking change for 4.0 | 1.0 | Cleanup flow control options during port construction - We have [flags, an array, and a boolean](https://github.com/EmergingTechnologyAdvisors/node-serialport/blob/3.1.2/README.md#serialport-path-options-openimmediately-callback) to set the flow control flags on a port. Lets keep it just the flags.
This would be a breaking change for 4.0 | non_priority | cleanup flow control options during port construction we have to set the flow control flags on a port lets keep it just the flags this would be a breaking change for | 0 |
255,178 | 19,295,304,276 | IssuesEvent | 2021-12-12 13:43:57 | The-OpenROAD-Project/OpenLane | https://api.github.com/repos/The-OpenROAD-Project/OpenLane | closed | Provide detailed instructions for makefile to support docker connection to XServer | documentation Docker Makefile | Provide clear and detailed instructions for running GUIs within the docker- specifically for Xserver support. Merely, setting the DISPLAY variable is not sufficient. The docker cmd needs a -e variable, for e.g
docker run -v /tmp/.X11-unix:/tmp/.X11-unix -e DISPLAY=unix:1 -it --rm -v $(OPENLANE_DIR):/openLANE_flow [...]
This is necessary for remote machine operation and will save first time users a lot of time
A useful link: https://l10nn.medium.com/running-x11-applications-with-docker-75133178d090
| 1.0 | Provide detailed instructions for makefile to support docker connection to XServer - Provide clear and detailed instructions for running GUIs within the docker- specifically for Xserver support. Merely, setting the DISPLAY variable is not sufficient. The docker cmd needs a -e variable, for e.g
docker run -v /tmp/.X11-unix:/tmp/.X11-unix -e DISPLAY=unix:1 -it --rm -v $(OPENLANE_DIR):/openLANE_flow [...]
This is necessary for remote machine operation and will save first time users a lot of time
A useful link: https://l10nn.medium.com/running-x11-applications-with-docker-75133178d090
| non_priority | provide detailed instructions for makefile to support docker connection to xserver provide clear and detailed instructions for running guis within the docker specifically for xserver support merely setting the display variable is not sufficient the docker cmd needs a e variable for e g docker run v tmp unix tmp unix e display unix it rm v openlane dir openlane flow this is necessary for remote machine operation and will save first time users a lot of time a useful link | 0 |
102,599 | 8,850,246,411 | IssuesEvent | 2019-01-08 12:43:07 | damianmoore/photo-manager | https://api.github.com/repos/damianmoore/photo-manager | opened | Tests to prove all models work | backend testing | Given known test images, the models should produce repeatable output. Their score, significance and returned data structure should be the same.
Models should be tested to run under multiple scenarios:
- [ ] Passing in a file path
- [ ] Passing in a Photo ID
- [ ] Passing in a Photo instance
- [ ] Running as from command line
- [ ] Running as from a job queue worker
Models covered:
- [ ] Object detection
- [ ] Style classification
- [ ] Color
- [ ] Location | 1.0 | Tests to prove all models work - Given known test images, the models should produce repeatable output. Their score, significance and returned data structure should be the same.
Models should be tested to run under multiple scenarios:
- [ ] Passing in a file path
- [ ] Passing in a Photo ID
- [ ] Passing in a Photo instance
- [ ] Running as from command line
- [ ] Running as from a job queue worker
Models covered:
- [ ] Object detection
- [ ] Style classification
- [ ] Color
- [ ] Location | non_priority | tests to prove all models work given known test images the models should produce repeatable output their score significance and returned data structure should be the same models should be tested to run under multiple scenarios passing in a file path passing in a photo id passing in a photo instance running as from command line running as from a job queue worker models covered object detection style classification color location | 0 |
56,137 | 6,502,263,764 | IssuesEvent | 2017-08-23 13:04:16 | dotnet/corefx | https://api.github.com/repos/dotnet/corefx | closed | Test failure: System.Runtime.Serialization.Formatters.Tests.BinaryFormatterTests/ValidateAgainstBlobs(obj: CookieContainer { Capacity = 10, Count = 1, MaxCookieSize = 1024, PerDomainCapacity = 5 }, blobs: [... | area-System.Runtime os-mac-os-x os-windows-uwp test bug test-run-core test-run-uwp-coreclr | Opened on behalf of @danmosemsft
The test `System.Runtime.Serialization.Formatters.Tests.BinaryFormatterTests/ValidateAgainstBlobs(obj: CookieContainer { Capacity = 10, Count = 1, MaxCookieSize = 1024, PerDomainCapacity = 5 }, blobs: [...` has failed.
The stored blob for type System.Net.CookieContainer is outdated and needs to be updated.
Stored blob: AAEAAAD/////AQAAAAAAAAAMAgAAAElTeXN0ZW0sIFZlcnNpb249NC4wLjAuMCwgQ3VsdHVyZT1uZXV0cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdhNWM1NjE5MzRlMDg5BQEAAAAaU3lzdGVtLk5ldC5Db29raWVDb250YWluZXIGAAAADW1fZG9tYWluVGFibGUPbV9tYXhDb29raWVTaXplDG1fbWF4Q29va2llcxVtX21heENvb2tpZXNQZXJEb21haW4HbV9jb3VudA5tX2ZxZG5NeURvbWFpbgMAAAAAARxTeXN0ZW0uQ29sbGVjdGlvbnMuSGFzaHRhYmxlCAgICAIAAAAJAwAAAAAEAAAKAAAABQAAAAEAAAAGBAAAAAAEAwAAABxTeXN0ZW0uQ29sbGVjdGlvbnMuSGFzaHRhYmxlBwAAAApMb2FkRmFjdG9yB1ZlcnNpb24IQ29tcGFyZXIQSGFzaENvZGVQcm92aWRlcghIYXNoU2l6ZQRLZXlzBlZhbHVlcwAAAwMABQULCBxTeXN0ZW0uQ29sbGVjdGlvbnMuSUNvbXBhcmVyJFN5c3RlbS5Db2xsZWN0aW9ucy5JSGFzaENvZGVQcm92aWRlcgjsUTg/AQAAAAoKAwAAAAkFAAAACQYAAAAQBQAAAAEAAAAGBwAAAAouMTI3LjAuMC4xEAYAAAABAAAACQgAAAAFCAAAABNTeXN0ZW0uTmV0LlBhdGhMaXN0AQAAAAZtX2xpc3QDLFN5c3RlbS5Db2xsZWN0aW9ucy5Tb3J0ZWRMaXN0K1N5bmNTb3J0ZWRMaXN0AgAAAAkJAAAABAkAAAAsU3lzdGVtLkNvbGxlY3Rpb25zLlNvcnRlZExpc3QrU3luY1NvcnRlZExpc3QJAAAABV9saXN0BV9yb290D1NvcnRlZExpc3Qra2V5cxFTb3J0ZWRMaXN0K3ZhbHVlcxBTb3J0ZWRMaXN0K19zaXplElNvcnRlZExpc3QrdmVyc2lvbhNTb3J0ZWRMaXN0K2NvbXBhcmVyElNvcnRlZExpc3Qra2V5TGlzdBRTb3J0ZWRMaXN0K3ZhbHVlTGlzdAMCBQUAAAMDAx1TeXN0ZW0uQ29sbGVjdGlvbnMuU29ydGVkTGlzdAgIG1N5c3RlbS5Db2xsZWN0aW9ucy5Db21wYXJlciVTeXN0ZW0uQ29sbGVjdGlvbnMuU29ydGVkTGlzdCtLZXlMaXN0J1N5c3RlbS5Db2xsZWN0aW9ucy5Tb3J0ZWRMaXN0K1ZhbHVlTGlzdAkKAAAACQsAAAAJDAAAAAkMAAAAAAAAAAAAAAAJDQAAAAoKBAoAAAAdU3lzdGVtLkNvbGxlY3Rpb25zLlNvcnRlZExpc3QHAAAABGtleXMGdmFsdWVzBV9zaXplB3ZlcnNpb24IY29tcGFyZXIHa2V5TGlzdAl2YWx1ZUxpc3QFBQAABAMDCAgkU3lzdGVtLk5ldC5QYXRoTGlzdCtQYXRoTGlzdENvbXBhcmVyAgAAACVTeXN0ZW0uQ29sbGVjdGlvbnMuU29ydGVkTGlzdCtLZXlMaXN0J1N5c3RlbS5Db2xsZWN0aW9ucy5Tb3J0ZWRMaXN0K1ZhbHVlTGlzdAkOAAAACQ8AAAABAAAAAQAAAAkQAAAACgkRAAAABAsAAAANU3lzdGVtLk9iamVjdAAAAAAQDAAAAAAAAAAEDQAAABtTeXN0ZW0uQ29sbGVjdGlvbnMuQ29tcGFyZXIBAAAAC0NvbXBhcmVJbmZvAyBTeXN0ZW0uR2xvYmFsaXphdGlvbi5Db21wYXJlSW5mbwkSAAAAEA4AAAAQAAAABhMAAAAFL3BhdGgNDxAPAAAAEAAAAAkUAAAADQ8FEAAAACRTeXN0ZW0uTmV0LlBhdGhMaXN0K1BhdGhMaXN0Q29tcGFyZXIAAAAAAgAAAAQRAAAAJ1N5c3RlbS5Db2xsZWN0aW9ucy5Tb3J0ZWRMaXN0K1ZhbHVlTGlzdAEAAAAKc29ydGVkTGlzdAMdU3lzdGVtLkNvbGxlY3Rpb25zLlNvcnRlZExpc3QJCgAAAAQSAAAAIFN5c3RlbS5HbG9iYWxpemF0aW9uLkNvbXBhcmVJbmZvAwAAAAZtX25hbWUNbV9Tb3J0VmVyc2lvbgdjdWx0dXJlAQMAIFN5c3RlbS5HbG9iYWxpemF0aW9uLlNvcnRWZXJzaW9uCAYWAAAABWVuLVVTCgkEAAAFFAAAABtTeXN0ZW0uTmV0LkNvb2tpZUNvbGxlY3Rpb24EAAAABm1fbGlzdAltX3ZlcnNpb24LbV9UaW1lU3RhbXAUbV9oYXNfb3RoZXJfdmVyc2lvbnMDAAAAHFN5c3RlbS5Db2xsZWN0aW9ucy5BcnJheUxpc3QIDQECAAAACRcAAAABAAAAAAAAAAAAAAABBBcAAAAcU3lzdGVtLkNvbGxlY3Rpb25zLkFycmF5TGlzdAMAAAAGX2l0ZW1zBV9zaXplCF92ZXJzaW9uBQAACAgJGAAAAAEAAAABAAAAEBgAAAAEAAAACRkAAAANAwUZAAAAEVN5c3RlbS5OZXQuQ29va2llFQAAAAltX2NvbW1lbnQMbV9jb21tZW50VXJpD21fY29va2llVmFyaWFudAltX2Rpc2NhcmQIbV9kb21haW4RbV9kb21haW5faW1wbGljaXQJbV9leHBpcmVzBm1fbmFtZQZtX3BhdGgPbV9wYXRoX2ltcGxpY2l0Bm1fcG9ydA9tX3BvcnRfaW1wbGljaXQLbV9wb3J0X2xpc3QIbV9zZWN1cmUKbV9odHRwT25seQttX3RpbWVTdGFtcAdtX3ZhbHVlCW1fdmVyc2lvbgttX2RvbWFpbktleQ9Jc1F1b3RlZFZlcnNpb24OSXNRdW90ZWREb21haW4BBAQAAQAAAQEAAQAHAAAAAQABAAAKU3lzdGVtLlVyaQIAAAAYU3lzdGVtLk5ldC5Db29raWVWYXJpYW50AgAAAAEBDQEBCAEBDQgBAQIAAAAJBAAAAAoF5f///xhTeXN0ZW0uTmV0LkNvb2tpZVZhcmlhbnQBAAAAB3ZhbHVlX18ACAIAAAABAAAAAAYcAAAACTEyNy4wLjAuMQAAAAAAAAAAAAYdAAAABW5hbWUxCRMAAAAACQQAAAABCgAAgFhsCQ2+tQgGIAAAAAV2YWx1ZQAAAAAJBwAAAAAACw==
Generated runtime blob: AAEAAAD/////AQAAAAAAAAAMAgAAAElTeXN0ZW0sIFZlcnNpb249NC4wLjAuMCwgQ3VsdHVyZT1uZXV0cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdhNWM1NjE5MzRlMDg5BQEAAAAaU3lzdGVtLk5ldC5Db29raWVDb250YWluZXIGAAAADW1fZG9tYWluVGFibGUPbV9tYXhDb29raWVTaXplDG1fbWF4Q29va2llcxVtX21heENvb2tpZXNQZXJEb21haW4HbV9jb3VudA5tX2ZxZG5NeURvbWFpbgMAAAAAARxTeXN0ZW0uQ29sbGVjdGlvbnMuSGFzaHRhYmxlCAgICAIAAAAJAwAAAAAEAAAKAAAABQAAAAEAAAAGBAAAAAAEAwAAABxTeXN0ZW0uQ29sbGVjdGlvbnMuSGFzaHRhYmxlBwAAAApMb2FkRmFjdG9yB1ZlcnNpb24IQ29tcGFyZXIQSGFzaENvZGVQcm92aWRlcghIYXNoU2l6ZQRLZXlzBlZhbHVlcwAAAwMABQULCBxTeXN0ZW0uQ29sbGVjdGlvbnMuSUNvbXBhcmVyJFN5c3RlbS5Db2xsZWN0aW9ucy5JSGFzaENvZGVQcm92aWRlcgjsUTg/AQAAAAoKAwAAAAkFAAAACQYAAAAQBQAAAAEAAAAGBwAAAAouMTI3LjAuMC4xEAYAAAABAAAACQgAAAAFCAAAABNTeXN0ZW0uTmV0LlBhdGhMaXN0AQAAAAZtX2xpc3QDLFN5c3RlbS5Db2xsZWN0aW9ucy5Tb3J0ZWRMaXN0K1N5bmNTb3J0ZWRMaXN0AgAAAAkJAAAABAkAAAAsU3lzdGVtLkNvbGxlY3Rpb25zLlNvcnRlZExpc3QrU3luY1NvcnRlZExpc3QJAAAABV9saXN0BV9yb290D1NvcnRlZExpc3Qra2V5cxFTb3J0ZWRMaXN0K3ZhbHVlcxBTb3J0ZWRMaXN0K19zaXplElNvcnRlZExpc3QrdmVyc2lvbhNTb3J0ZWRMaXN0K2NvbXBhcmVyElNvcnRlZExpc3Qra2V5TGlzdBRTb3J0ZWRMaXN0K3ZhbHVlTGlzdAMCBQUAAAMDAx1TeXN0ZW0uQ29sbGVjdGlvbnMuU29ydGVkTGlzdAgIG1N5c3RlbS5Db2xsZWN0aW9ucy5Db21wYXJlciVTeXN0ZW0uQ29sbGVjdGlvbnMuU29ydGVkTGlzdCtLZXlMaXN0J1N5c3RlbS5Db2xsZWN0aW9ucy5Tb3J0ZWRMaXN0K1ZhbHVlTGlzdAkKAAAACQsAAAAJDAAAAAkMAAAAAAAAAAAAAAAJDQAAAAoKBAoAAAAdU3lzdGVtLkNvbGxlY3Rpb25zLlNvcnRlZExpc3QHAAAABGtleXMGdmFsdWVzBV9zaXplB3ZlcnNpb24IY29tcGFyZXIHa2V5TGlzdAl2YWx1ZUxpc3QFBQAABAMDCAgkU3lzdGVtLk5ldC5QYXRoTGlzdCtQYXRoTGlzdENvbXBhcmVyAgAAACVTeXN0ZW0uQ29sbGVjdGlvbnMuU29ydGVkTGlzdCtLZXlMaXN0J1N5c3RlbS5Db2xsZWN0aW9ucy5Tb3J0ZWRMaXN0K1ZhbHVlTGlzdAkOAAAACQ8AAAABAAAAAQAAAAkQAAAACgkRAAAABAsAAAANU3lzdGVtLk9iamVjdAAAAAAQDAAAAAAAAAAEDQAAABtTeXN0ZW0uQ29sbGVjdGlvbnMuQ29tcGFyZXIBAAAAC0NvbXBhcmVJbmZvAyBTeXN0ZW0uR2xvYmFsaXphdGlvbi5Db21wYXJlSW5mbwkSAAAAEA4AAAAQAAAABhMAAAAFL3BhdGgNDxAPAAAAEAAAAAkUAAAADQ8FEAAAACRTeXN0ZW0uTmV0LlBhdGhMaXN0K1BhdGhMaXN0Q29tcGFyZXIAAAAAAgAAAAQRAAAAJ1N5c3RlbS5Db2xsZWN0aW9ucy5Tb3J0ZWRMaXN0K1ZhbHVlTGlzdAEAAAAKc29ydGVkTGlzdAMdU3lzdGVtLkNvbGxlY3Rpb25zLlNvcnRlZExpc3QJCgAAAAQSAAAAIFN5c3RlbS5HbG9iYWxpemF0aW9uLkNvbXBhcmVJbmZvAwAAAAZtX25hbWUNbV9Tb3J0VmVyc2lvbgdjdWx0dXJlAQMAIFN5c3RlbS5HbG9iYWxpemF0aW9uLlNvcnRWZXJzaW9uCAkEAAAACn8AAAAFFAAAABtTeXN0ZW0uTmV0LkNvb2tpZUNvbGxlY3Rpb24EAAAABm1fbGlzdAltX3ZlcnNpb24LbV9UaW1lU3RhbXAUbV9oYXNfb3RoZXJfdmVyc2lvbnMDAAAAHFN5c3RlbS5Db2xsZWN0aW9ucy5BcnJheUxpc3QIDQECAAAACRcAAAABAAAAAAAAAAAAAAABBBcAAAAcU3lzdGVtLkNvbGxlY3Rpb25zLkFycmF5TGlzdAMAAAAGX2l0ZW1zBV9zaXplCF92ZXJzaW9uBQAACAgJGAAAAAEAAAABAAAAEBgAAAAEAAAACRkAAAANAwUZAAAAEVN5c3RlbS5OZXQuQ29va2llFQAAAAltX2NvbW1lbnQMbV9jb21tZW50VXJpD21fY29va2llVmFyaWFudAltX2Rpc2NhcmQIbV9kb21haW4RbV9kb21haW5faW1wbGljaXQJbV9leHBpcmVzBm1fbmFtZQZtX3BhdGgPbV9wYXRoX2ltcGxpY2l0Bm1fcG9ydA9tX3BvcnRfaW1wbGljaXQLbV9wb3J0X2xpc3QIbV9zZWN1cmUKbV9odHRwT25seQttX3RpbWVTdGFtcAdtX3ZhbHVlCW1fdmVyc2lvbgttX2RvbWFpbktleQ9Jc1F1b3RlZFZlcnNpb24OSXNRdW90ZWREb21haW4BBAQAAQAAAQEAAQAHAAAAAQABAAAKU3lzdGVtLlVyaQIAAAAYU3lzdGVtLk5ldC5Db29raWVWYXJpYW50AgAAAAEBDQEBCAEBDQgBAQIAAAAJBAAAAAoF5f///xhTeXN0ZW0uTmV0LkNvb2tpZVZhcmlhbnQBAAAAB3ZhbHVlX18ACAIAAAABAAAAAAYcAAAACTEyNy4wLjAuMQAAAAAAAAAAAAYdAAAABW5hbWUxCRMAAAAACQQAAAABCgAAgFhsCQ2+tQgGIAAAAAV2YWx1ZQAAAAAJBwAAAAAACw==
Expected: True
Actual: False
Stack Trace:
at System.Runtime.Serialization.Formatters.Tests.BinaryFormatterTests.ValidateAgainstBlobs(Object obj, String[] blobs) in /Users/buildagent/agent/_work/45/s/corefx/src/System.Runtime.Serialization.Formatters/tests/BinaryFormatterTests.cs:line 62
Build : Master - 20170626.01 (Core Tests)
Failing configurations:
- OSX.1013.Amd64-x64
- Release
- OSX.1012.Amd64-x64
- Release
| 3.0 | Test failure: System.Runtime.Serialization.Formatters.Tests.BinaryFormatterTests/ValidateAgainstBlobs(obj: CookieContainer { Capacity = 10, Count = 1, MaxCookieSize = 1024, PerDomainCapacity = 5 }, blobs: [... - Opened on behalf of @danmosemsft
The test `System.Runtime.Serialization.Formatters.Tests.BinaryFormatterTests/ValidateAgainstBlobs(obj: CookieContainer { Capacity = 10, Count = 1, MaxCookieSize = 1024, PerDomainCapacity = 5 }, blobs: [...` has failed.
The stored blob for type System.Net.CookieContainer is outdated and needs to be updated.
Stored blob: AAEAAAD/////AQAAAAAAAAAMAgAAAElTeXN0ZW0sIFZlcnNpb249NC4wLjAuMCwgQ3VsdHVyZT1uZXV0cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdhNWM1NjE5MzRlMDg5BQEAAAAaU3lzdGVtLk5ldC5Db29raWVDb250YWluZXIGAAAADW1fZG9tYWluVGFibGUPbV9tYXhDb29raWVTaXplDG1fbWF4Q29va2llcxVtX21heENvb2tpZXNQZXJEb21haW4HbV9jb3VudA5tX2ZxZG5NeURvbWFpbgMAAAAAARxTeXN0ZW0uQ29sbGVjdGlvbnMuSGFzaHRhYmxlCAgICAIAAAAJAwAAAAAEAAAKAAAABQAAAAEAAAAGBAAAAAAEAwAAABxTeXN0ZW0uQ29sbGVjdGlvbnMuSGFzaHRhYmxlBwAAAApMb2FkRmFjdG9yB1ZlcnNpb24IQ29tcGFyZXIQSGFzaENvZGVQcm92aWRlcghIYXNoU2l6ZQRLZXlzBlZhbHVlcwAAAwMABQULCBxTeXN0ZW0uQ29sbGVjdGlvbnMuSUNvbXBhcmVyJFN5c3RlbS5Db2xsZWN0aW9ucy5JSGFzaENvZGVQcm92aWRlcgjsUTg/AQAAAAoKAwAAAAkFAAAACQYAAAAQBQAAAAEAAAAGBwAAAAouMTI3LjAuMC4xEAYAAAABAAAACQgAAAAFCAAAABNTeXN0ZW0uTmV0LlBhdGhMaXN0AQAAAAZtX2xpc3QDLFN5c3RlbS5Db2xsZWN0aW9ucy5Tb3J0ZWRMaXN0K1N5bmNTb3J0ZWRMaXN0AgAAAAkJAAAABAkAAAAsU3lzdGVtLkNvbGxlY3Rpb25zLlNvcnRlZExpc3QrU3luY1NvcnRlZExpc3QJAAAABV9saXN0BV9yb290D1NvcnRlZExpc3Qra2V5cxFTb3J0ZWRMaXN0K3ZhbHVlcxBTb3J0ZWRMaXN0K19zaXplElNvcnRlZExpc3QrdmVyc2lvbhNTb3J0ZWRMaXN0K2NvbXBhcmVyElNvcnRlZExpc3Qra2V5TGlzdBRTb3J0ZWRMaXN0K3ZhbHVlTGlzdAMCBQUAAAMDAx1TeXN0ZW0uQ29sbGVjdGlvbnMuU29ydGVkTGlzdAgIG1N5c3RlbS5Db2xsZWN0aW9ucy5Db21wYXJlciVTeXN0ZW0uQ29sbGVjdGlvbnMuU29ydGVkTGlzdCtLZXlMaXN0J1N5c3RlbS5Db2xsZWN0aW9ucy5Tb3J0ZWRMaXN0K1ZhbHVlTGlzdAkKAAAACQsAAAAJDAAAAAkMAAAAAAAAAAAAAAAJDQAAAAoKBAoAAAAdU3lzdGVtLkNvbGxlY3Rpb25zLlNvcnRlZExpc3QHAAAABGtleXMGdmFsdWVzBV9zaXplB3ZlcnNpb24IY29tcGFyZXIHa2V5TGlzdAl2YWx1ZUxpc3QFBQAABAMDCAgkU3lzdGVtLk5ldC5QYXRoTGlzdCtQYXRoTGlzdENvbXBhcmVyAgAAACVTeXN0ZW0uQ29sbGVjdGlvbnMuU29ydGVkTGlzdCtLZXlMaXN0J1N5c3RlbS5Db2xsZWN0aW9ucy5Tb3J0ZWRMaXN0K1ZhbHVlTGlzdAkOAAAACQ8AAAABAAAAAQAAAAkQAAAACgkRAAAABAsAAAANU3lzdGVtLk9iamVjdAAAAAAQDAAAAAAAAAAEDQAAABtTeXN0ZW0uQ29sbGVjdGlvbnMuQ29tcGFyZXIBAAAAC0NvbXBhcmVJbmZvAyBTeXN0ZW0uR2xvYmFsaXphdGlvbi5Db21wYXJlSW5mbwkSAAAAEA4AAAAQAAAABhMAAAAFL3BhdGgNDxAPAAAAEAAAAAkUAAAADQ8FEAAAACRTeXN0ZW0uTmV0LlBhdGhMaXN0K1BhdGhMaXN0Q29tcGFyZXIAAAAAAgAAAAQRAAAAJ1N5c3RlbS5Db2xsZWN0aW9ucy5Tb3J0ZWRMaXN0K1ZhbHVlTGlzdAEAAAAKc29ydGVkTGlzdAMdU3lzdGVtLkNvbGxlY3Rpb25zLlNvcnRlZExpc3QJCgAAAAQSAAAAIFN5c3RlbS5HbG9iYWxpemF0aW9uLkNvbXBhcmVJbmZvAwAAAAZtX25hbWUNbV9Tb3J0VmVyc2lvbgdjdWx0dXJlAQMAIFN5c3RlbS5HbG9iYWxpemF0aW9uLlNvcnRWZXJzaW9uCAYWAAAABWVuLVVTCgkEAAAFFAAAABtTeXN0ZW0uTmV0LkNvb2tpZUNvbGxlY3Rpb24EAAAABm1fbGlzdAltX3ZlcnNpb24LbV9UaW1lU3RhbXAUbV9oYXNfb3RoZXJfdmVyc2lvbnMDAAAAHFN5c3RlbS5Db2xsZWN0aW9ucy5BcnJheUxpc3QIDQECAAAACRcAAAABAAAAAAAAAAAAAAABBBcAAAAcU3lzdGVtLkNvbGxlY3Rpb25zLkFycmF5TGlzdAMAAAAGX2l0ZW1zBV9zaXplCF92ZXJzaW9uBQAACAgJGAAAAAEAAAABAAAAEBgAAAAEAAAACRkAAAANAwUZAAAAEVN5c3RlbS5OZXQuQ29va2llFQAAAAltX2NvbW1lbnQMbV9jb21tZW50VXJpD21fY29va2llVmFyaWFudAltX2Rpc2NhcmQIbV9kb21haW4RbV9kb21haW5faW1wbGljaXQJbV9leHBpcmVzBm1fbmFtZQZtX3BhdGgPbV9wYXRoX2ltcGxpY2l0Bm1fcG9ydA9tX3BvcnRfaW1wbGljaXQLbV9wb3J0X2xpc3QIbV9zZWN1cmUKbV9odHRwT25seQttX3RpbWVTdGFtcAdtX3ZhbHVlCW1fdmVyc2lvbgttX2RvbWFpbktleQ9Jc1F1b3RlZFZlcnNpb24OSXNRdW90ZWREb21haW4BBAQAAQAAAQEAAQAHAAAAAQABAAAKU3lzdGVtLlVyaQIAAAAYU3lzdGVtLk5ldC5Db29raWVWYXJpYW50AgAAAAEBDQEBCAEBDQgBAQIAAAAJBAAAAAoF5f///xhTeXN0ZW0uTmV0LkNvb2tpZVZhcmlhbnQBAAAAB3ZhbHVlX18ACAIAAAABAAAAAAYcAAAACTEyNy4wLjAuMQAAAAAAAAAAAAYdAAAABW5hbWUxCRMAAAAACQQAAAABCgAAgFhsCQ2+tQgGIAAAAAV2YWx1ZQAAAAAJBwAAAAAACw==
Generated runtime blob: AAEAAAD/////AQAAAAAAAAAMAgAAAElTeXN0ZW0sIFZlcnNpb249NC4wLjAuMCwgQ3VsdHVyZT1uZXV0cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdhNWM1NjE5MzRlMDg5BQEAAAAaU3lzdGVtLk5ldC5Db29raWVDb250YWluZXIGAAAADW1fZG9tYWluVGFibGUPbV9tYXhDb29raWVTaXplDG1fbWF4Q29va2llcxVtX21heENvb2tpZXNQZXJEb21haW4HbV9jb3VudA5tX2ZxZG5NeURvbWFpbgMAAAAAARxTeXN0ZW0uQ29sbGVjdGlvbnMuSGFzaHRhYmxlCAgICAIAAAAJAwAAAAAEAAAKAAAABQAAAAEAAAAGBAAAAAAEAwAAABxTeXN0ZW0uQ29sbGVjdGlvbnMuSGFzaHRhYmxlBwAAAApMb2FkRmFjdG9yB1ZlcnNpb24IQ29tcGFyZXIQSGFzaENvZGVQcm92aWRlcghIYXNoU2l6ZQRLZXlzBlZhbHVlcwAAAwMABQULCBxTeXN0ZW0uQ29sbGVjdGlvbnMuSUNvbXBhcmVyJFN5c3RlbS5Db2xsZWN0aW9ucy5JSGFzaENvZGVQcm92aWRlcgjsUTg/AQAAAAoKAwAAAAkFAAAACQYAAAAQBQAAAAEAAAAGBwAAAAouMTI3LjAuMC4xEAYAAAABAAAACQgAAAAFCAAAABNTeXN0ZW0uTmV0LlBhdGhMaXN0AQAAAAZtX2xpc3QDLFN5c3RlbS5Db2xsZWN0aW9ucy5Tb3J0ZWRMaXN0K1N5bmNTb3J0ZWRMaXN0AgAAAAkJAAAABAkAAAAsU3lzdGVtLkNvbGxlY3Rpb25zLlNvcnRlZExpc3QrU3luY1NvcnRlZExpc3QJAAAABV9saXN0BV9yb290D1NvcnRlZExpc3Qra2V5cxFTb3J0ZWRMaXN0K3ZhbHVlcxBTb3J0ZWRMaXN0K19zaXplElNvcnRlZExpc3QrdmVyc2lvbhNTb3J0ZWRMaXN0K2NvbXBhcmVyElNvcnRlZExpc3Qra2V5TGlzdBRTb3J0ZWRMaXN0K3ZhbHVlTGlzdAMCBQUAAAMDAx1TeXN0ZW0uQ29sbGVjdGlvbnMuU29ydGVkTGlzdAgIG1N5c3RlbS5Db2xsZWN0aW9ucy5Db21wYXJlciVTeXN0ZW0uQ29sbGVjdGlvbnMuU29ydGVkTGlzdCtLZXlMaXN0J1N5c3RlbS5Db2xsZWN0aW9ucy5Tb3J0ZWRMaXN0K1ZhbHVlTGlzdAkKAAAACQsAAAAJDAAAAAkMAAAAAAAAAAAAAAAJDQAAAAoKBAoAAAAdU3lzdGVtLkNvbGxlY3Rpb25zLlNvcnRlZExpc3QHAAAABGtleXMGdmFsdWVzBV9zaXplB3ZlcnNpb24IY29tcGFyZXIHa2V5TGlzdAl2YWx1ZUxpc3QFBQAABAMDCAgkU3lzdGVtLk5ldC5QYXRoTGlzdCtQYXRoTGlzdENvbXBhcmVyAgAAACVTeXN0ZW0uQ29sbGVjdGlvbnMuU29ydGVkTGlzdCtLZXlMaXN0J1N5c3RlbS5Db2xsZWN0aW9ucy5Tb3J0ZWRMaXN0K1ZhbHVlTGlzdAkOAAAACQ8AAAABAAAAAQAAAAkQAAAACgkRAAAABAsAAAANU3lzdGVtLk9iamVjdAAAAAAQDAAAAAAAAAAEDQAAABtTeXN0ZW0uQ29sbGVjdGlvbnMuQ29tcGFyZXIBAAAAC0NvbXBhcmVJbmZvAyBTeXN0ZW0uR2xvYmFsaXphdGlvbi5Db21wYXJlSW5mbwkSAAAAEA4AAAAQAAAABhMAAAAFL3BhdGgNDxAPAAAAEAAAAAkUAAAADQ8FEAAAACRTeXN0ZW0uTmV0LlBhdGhMaXN0K1BhdGhMaXN0Q29tcGFyZXIAAAAAAgAAAAQRAAAAJ1N5c3RlbS5Db2xsZWN0aW9ucy5Tb3J0ZWRMaXN0K1ZhbHVlTGlzdAEAAAAKc29ydGVkTGlzdAMdU3lzdGVtLkNvbGxlY3Rpb25zLlNvcnRlZExpc3QJCgAAAAQSAAAAIFN5c3RlbS5HbG9iYWxpemF0aW9uLkNvbXBhcmVJbmZvAwAAAAZtX25hbWUNbV9Tb3J0VmVyc2lvbgdjdWx0dXJlAQMAIFN5c3RlbS5HbG9iYWxpemF0aW9uLlNvcnRWZXJzaW9uCAkEAAAACn8AAAAFFAAAABtTeXN0ZW0uTmV0LkNvb2tpZUNvbGxlY3Rpb24EAAAABm1fbGlzdAltX3ZlcnNpb24LbV9UaW1lU3RhbXAUbV9oYXNfb3RoZXJfdmVyc2lvbnMDAAAAHFN5c3RlbS5Db2xsZWN0aW9ucy5BcnJheUxpc3QIDQECAAAACRcAAAABAAAAAAAAAAAAAAABBBcAAAAcU3lzdGVtLkNvbGxlY3Rpb25zLkFycmF5TGlzdAMAAAAGX2l0ZW1zBV9zaXplCF92ZXJzaW9uBQAACAgJGAAAAAEAAAABAAAAEBgAAAAEAAAACRkAAAANAwUZAAAAEVN5c3RlbS5OZXQuQ29va2llFQAAAAltX2NvbW1lbnQMbV9jb21tZW50VXJpD21fY29va2llVmFyaWFudAltX2Rpc2NhcmQIbV9kb21haW4RbV9kb21haW5faW1wbGljaXQJbV9leHBpcmVzBm1fbmFtZQZtX3BhdGgPbV9wYXRoX2ltcGxpY2l0Bm1fcG9ydA9tX3BvcnRfaW1wbGljaXQLbV9wb3J0X2xpc3QIbV9zZWN1cmUKbV9odHRwT25seQttX3RpbWVTdGFtcAdtX3ZhbHVlCW1fdmVyc2lvbgttX2RvbWFpbktleQ9Jc1F1b3RlZFZlcnNpb24OSXNRdW90ZWREb21haW4BBAQAAQAAAQEAAQAHAAAAAQABAAAKU3lzdGVtLlVyaQIAAAAYU3lzdGVtLk5ldC5Db29raWVWYXJpYW50AgAAAAEBDQEBCAEBDQgBAQIAAAAJBAAAAAoF5f///xhTeXN0ZW0uTmV0LkNvb2tpZVZhcmlhbnQBAAAAB3ZhbHVlX18ACAIAAAABAAAAAAYcAAAACTEyNy4wLjAuMQAAAAAAAAAAAAYdAAAABW5hbWUxCRMAAAAACQQAAAABCgAAgFhsCQ2+tQgGIAAAAAV2YWx1ZQAAAAAJBwAAAAAACw==
Expected: True
Actual: False
Stack Trace:
at System.Runtime.Serialization.Formatters.Tests.BinaryFormatterTests.ValidateAgainstBlobs(Object obj, String[] blobs) in /Users/buildagent/agent/_work/45/s/corefx/src/System.Runtime.Serialization.Formatters/tests/BinaryFormatterTests.cs:line 62
Build : Master - 20170626.01 (Core Tests)
Failing configurations:
- OSX.1013.Amd64-x64
- Release
- OSX.1012.Amd64-x64
- Release
| non_priority | test failure system runtime serialization formatters tests binaryformattertests validateagainstblobs obj cookiecontainer capacity count maxcookiesize perdomaincapacity blobs opened on behalf of danmosemsft the test system runtime serialization formatters tests binaryformattertests validateagainstblobs obj cookiecontainer capacity count maxcookiesize perdomaincapacity blobs has failed the stored blob for type system net cookiecontainer is outdated and needs to be updated stored blob aaeaaad generated runtime blob aaeaaad expected true actual false stack trace at system runtime serialization formatters tests binaryformattertests validateagainstblobs object obj string blobs in users buildagent agent work s corefx src system runtime serialization formatters tests binaryformattertests cs line build master core tests failing configurations osx release osx release | 0 |
4,036 | 6,259,152,150 | IssuesEvent | 2017-07-14 17:21:55 | HBHWoolacotts/RPii | https://api.github.com/repos/HBHWoolacotts/RPii | opened | Accept/Decline Buttons are HIDDEN in POS for HOME REPAIRS - Please Show Them | Label: Service | This was done by design as Tara originally managed the Home Repairs.
Now that Estimates for these are going to the booking location, we would like the Shops to be able to Accept or Decline the estimates, so please can these buttons be enabled.
Do they send an email and if yes who to please? | 1.0 | Accept/Decline Buttons are HIDDEN in POS for HOME REPAIRS - Please Show Them - This was done by design as Tara originally managed the Home Repairs.
Now that Estimates for these are going to the booking location, we would like the Shops to be able to Accept or Decline the estimates, so please can these buttons be enabled.
Do they send an email and if yes who to please? | non_priority | accept decline buttons are hidden in pos for home repairs please show them this was done by design as tara originally managed the home repairs now that estimates for these are going to the booking location we would like the shops to be able to accept or decline the estimates so please can these buttons be enabled do they send an email and if yes who to please | 0 |
99,262 | 16,440,436,629 | IssuesEvent | 2021-05-20 13:50:41 | project-chip/connectedhomeip | https://api.github.com/repos/project-chip/connectedhomeip | closed | Please use MemoryCalloc to help ensure that in bad logic further down, we at least have deterministic 0's in the spots that may be skipped or otherwise incorrectly used, rather than random garbage. | memory security | Please use MemoryCalloc to help ensure that in bad logic further down, we at least have deterministic 0's in the spots that may be skipped or otherwise incorrectly used, rather than random garbage.
_Originally posted by @tcarmelveilleux in https://github.com/project-chip/connectedhomeip/pull/6800#discussion_r632537205_ | True | Please use MemoryCalloc to help ensure that in bad logic further down, we at least have deterministic 0's in the spots that may be skipped or otherwise incorrectly used, rather than random garbage. - Please use MemoryCalloc to help ensure that in bad logic further down, we at least have deterministic 0's in the spots that may be skipped or otherwise incorrectly used, rather than random garbage.
_Originally posted by @tcarmelveilleux in https://github.com/project-chip/connectedhomeip/pull/6800#discussion_r632537205_ | non_priority | please use memorycalloc to help ensure that in bad logic further down we at least have deterministic s in the spots that may be skipped or otherwise incorrectly used rather than random garbage please use memorycalloc to help ensure that in bad logic further down we at least have deterministic s in the spots that may be skipped or otherwise incorrectly used rather than random garbage originally posted by tcarmelveilleux in | 0 |
205,811 | 15,689,755,775 | IssuesEvent | 2021-03-25 15:59:57 | dso-toolkit/dso-toolkit | https://api.github.com/repos/dso-toolkit/dso-toolkit | closed | Visited state in Tabs verwijderen | package/dso-toolkit status:testable type:improvement | Het is niet wenselijk dat de links in de tabs component een herkenbare 'visited state' styling krijgen (dit is niet wenselijk, omdat het "navigatie menu links" betreft). De links in de tab moeten donkergrijs `#666666` blijven.
URL in DSO Toolkit : https://dso-toolkit.nl/master/components/detail/tabs.html
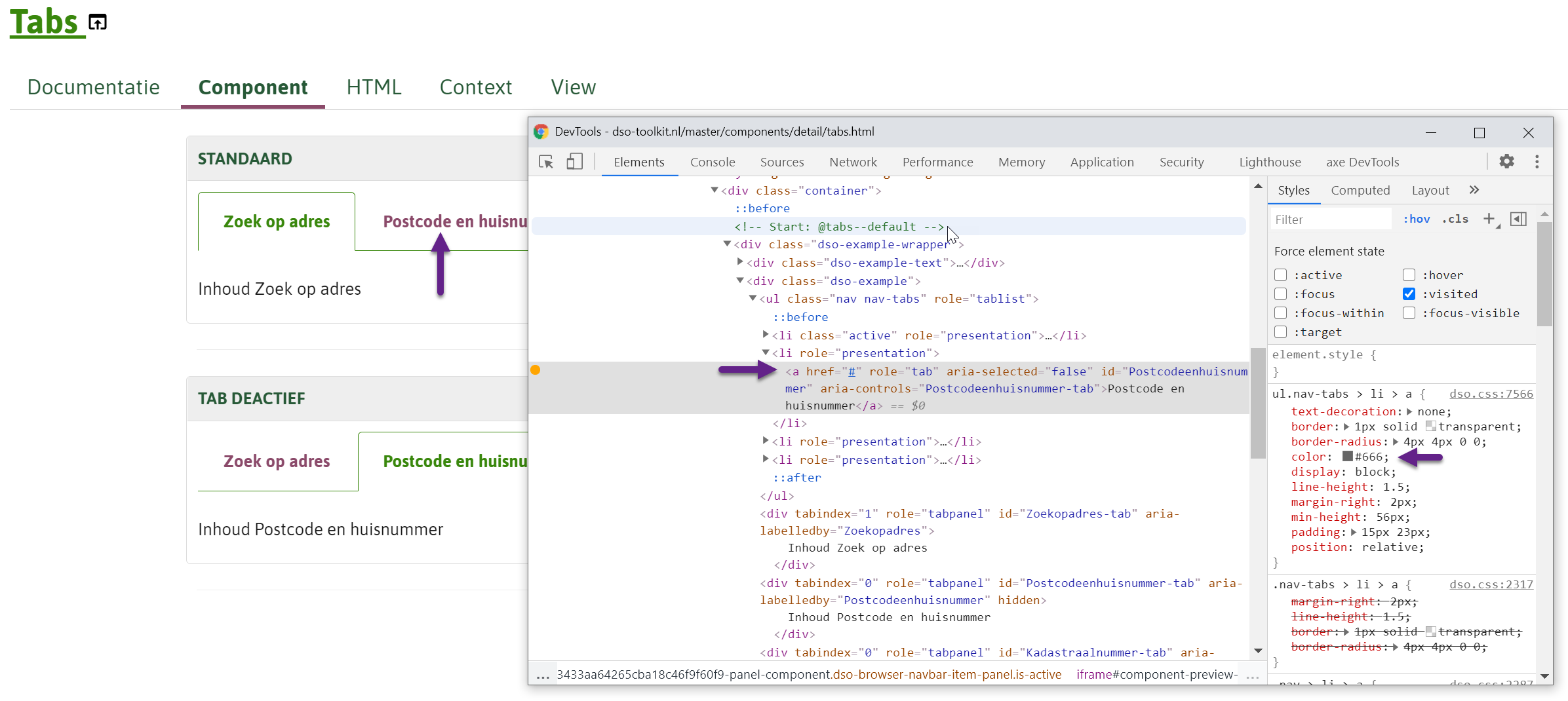
NB: het huidige 'paars' lijkt default-browser styling te zijn.
Hoe te testen:
Klik eenmaal op een van de links in de tabs. Foutsituatie (huidig) is dat de link verkleurt. Goedsituatie na change is dat de link donkergrijs blijft. | 1.0 | Visited state in Tabs verwijderen - Het is niet wenselijk dat de links in de tabs component een herkenbare 'visited state' styling krijgen (dit is niet wenselijk, omdat het "navigatie menu links" betreft). De links in de tab moeten donkergrijs `#666666` blijven.
URL in DSO Toolkit : https://dso-toolkit.nl/master/components/detail/tabs.html
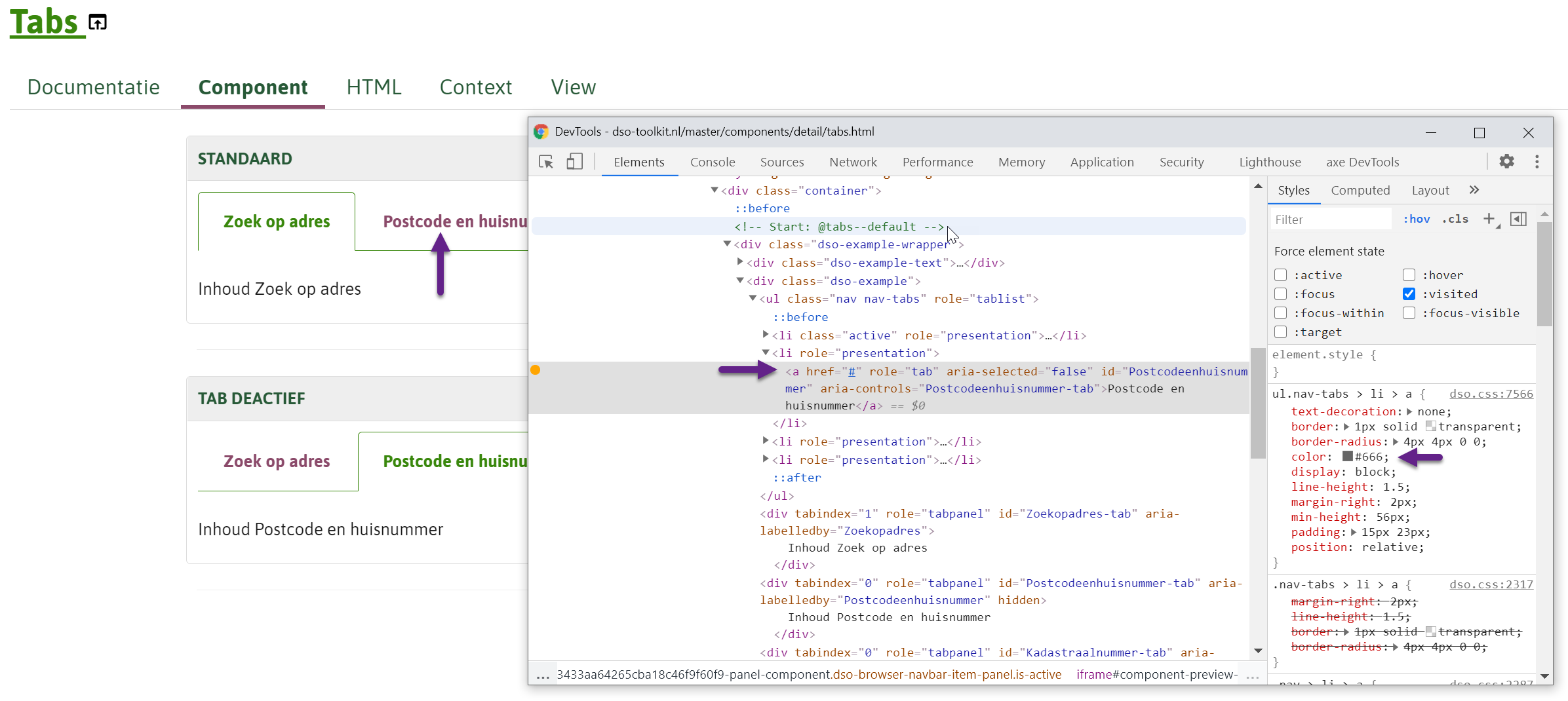
NB: het huidige 'paars' lijkt default-browser styling te zijn.
Hoe te testen:
Klik eenmaal op een van de links in de tabs. Foutsituatie (huidig) is dat de link verkleurt. Goedsituatie na change is dat de link donkergrijs blijft. | non_priority | visited state in tabs verwijderen het is niet wenselijk dat de links in de tabs component een herkenbare visited state styling krijgen dit is niet wenselijk omdat het navigatie menu links betreft de links in de tab moeten donkergrijs blijven url in dso toolkit nb het huidige paars lijkt default browser styling te zijn hoe te testen klik eenmaal op een van de links in de tabs foutsituatie huidig is dat de link verkleurt goedsituatie na change is dat de link donkergrijs blijft | 0 |
325,064 | 27,846,285,491 | IssuesEvent | 2023-03-20 15:41:22 | BoBAdministration/QA-Bug-Reports | https://api.github.com/repos/BoBAdministration/QA-Bug-Reports | closed | Icons duplicate and get stuck on the screen | Fixed-PendingTesting | **Describe the Bug**
players icons get stuck on your screen if a player respawn in the egg that's in your group
**To Reproduce**
1. get a group with the eggs
2. have 1 or more players take these eggs and force respawn in it
3. repeat this process a few times, by laying new eggs and giving them to a players that force respawn in it
4. let one of this players that is been taking the eggs join your group and hang around
5. this player in your group will randomly start to duplicate it's icon anywhere it walks
**Expected behavior**
icons should duplicate this way
**Actual behavior**
it duplicates
**Screenshots & Video**
https://yapx.ru/u/QJyKn
**Additional info**
This icons can't be hidden with an I button
**Branch Version**
live and tester
| 1.0 | Icons duplicate and get stuck on the screen - **Describe the Bug**
players icons get stuck on your screen if a player respawn in the egg that's in your group
**To Reproduce**
1. get a group with the eggs
2. have 1 or more players take these eggs and force respawn in it
3. repeat this process a few times, by laying new eggs and giving them to a players that force respawn in it
4. let one of this players that is been taking the eggs join your group and hang around
5. this player in your group will randomly start to duplicate it's icon anywhere it walks
**Expected behavior**
icons should duplicate this way
**Actual behavior**
it duplicates
**Screenshots & Video**
https://yapx.ru/u/QJyKn
**Additional info**
This icons can't be hidden with an I button
**Branch Version**
live and tester
| non_priority | icons duplicate and get stuck on the screen describe the bug players icons get stuck on your screen if a player respawn in the egg that s in your group to reproduce get a group with the eggs have or more players take these eggs and force respawn in it repeat this process a few times by laying new eggs and giving them to a players that force respawn in it let one of this players that is been taking the eggs join your group and hang around this player in your group will randomly start to duplicate it s icon anywhere it walks expected behavior icons should duplicate this way actual behavior it duplicates screenshots video additional info this icons can t be hidden with an i button branch version live and tester | 0 |
271,129 | 23,583,983,477 | IssuesEvent | 2022-08-23 09:59:08 | quarkusio/quarkus | https://api.github.com/repos/quarkusio/quarkus | closed | @TestHTTPResource annotation injects endpoint URL without the quarkus.http.root-path segment | kind/bug area/testing | ### Describe the bug
When injecting an endpoint URL in test using the `io.quarkus.test.common.http.TestHTTPResource` annotation, the injected path does not contain a segment, specified by the `quarkus.http.root-path` config property.
### Expected behavior
A full enpoint URL with, including the value of `quarkus.http.root-path`, should be injected.
### Actual behavior
The injected URL lacks the `quarkus.http.root-path` segment.
### How to Reproduce?
```
@TestHTTPEndpoint(MyResource.class)
@TestHTTPResource
URL myResourceUrl;
```
The injected URL would lack the path segment set by the `quarkus.http.root-path` property.
### Output of `uname -a` or `ver`
Microsoft Windows [Version 10.0.19042.867]
### Output of `java -version`
openjdk version "18.0.2" 2022-07-19
### GraalVM version (if different from Java)
_No response_
### Quarkus version or git rev
2.11.2.Final
### Build tool (ie. output of `mvnw --version` or `gradlew --version`)
Gradle 7.5.1
### Additional information
It seems that this happens because the [`TestHTTPResourceManager`](https://github.com/quarkusio/quarkus/blob/b0b51fdc80024efea3acf114b13cd7eb688c5247/test-framework/common/src/main/java/io/quarkus/test/common/http/TestHTTPResourceManager.java#L23) class uses the `test.url` config property to determine an endpoint URL, which is, in turn, is provided by the [`TestHTTPConfigSourceProvider`](https://github.com/quarkusio/quarkus/blob/b0b51fdc80024efea3acf114b13cd7eb688c5247/test-framework/common/src/main/java/io/quarkus/test/common/http/TestHTTPConfigSourceProvider.java#L17) using the following expression:
```
"http://${quarkus.http.host:localhost}:${quarkus.http.test-port:8081}${quarkus.servlet.context-path:}"
```
As you can see, instead of the `quarkus.http.root-path`, the `quarkus.servlet.context-path` is used, which is not applicable for a standalone application.
A workaround is to set the `quarkus.servlet.context-path` in like this:
```
quarkus.servlet.context-path=${quarkus.http.root-path}
``` | 1.0 | @TestHTTPResource annotation injects endpoint URL without the quarkus.http.root-path segment - ### Describe the bug
When injecting an endpoint URL in test using the `io.quarkus.test.common.http.TestHTTPResource` annotation, the injected path does not contain a segment, specified by the `quarkus.http.root-path` config property.
### Expected behavior
A full enpoint URL with, including the value of `quarkus.http.root-path`, should be injected.
### Actual behavior
The injected URL lacks the `quarkus.http.root-path` segment.
### How to Reproduce?
```
@TestHTTPEndpoint(MyResource.class)
@TestHTTPResource
URL myResourceUrl;
```
The injected URL would lack the path segment set by the `quarkus.http.root-path` property.
### Output of `uname -a` or `ver`
Microsoft Windows [Version 10.0.19042.867]
### Output of `java -version`
openjdk version "18.0.2" 2022-07-19
### GraalVM version (if different from Java)
_No response_
### Quarkus version or git rev
2.11.2.Final
### Build tool (ie. output of `mvnw --version` or `gradlew --version`)
Gradle 7.5.1
### Additional information
It seems that this happens because the [`TestHTTPResourceManager`](https://github.com/quarkusio/quarkus/blob/b0b51fdc80024efea3acf114b13cd7eb688c5247/test-framework/common/src/main/java/io/quarkus/test/common/http/TestHTTPResourceManager.java#L23) class uses the `test.url` config property to determine an endpoint URL, which is, in turn, is provided by the [`TestHTTPConfigSourceProvider`](https://github.com/quarkusio/quarkus/blob/b0b51fdc80024efea3acf114b13cd7eb688c5247/test-framework/common/src/main/java/io/quarkus/test/common/http/TestHTTPConfigSourceProvider.java#L17) using the following expression:
```
"http://${quarkus.http.host:localhost}:${quarkus.http.test-port:8081}${quarkus.servlet.context-path:}"
```
As you can see, instead of the `quarkus.http.root-path`, the `quarkus.servlet.context-path` is used, which is not applicable for a standalone application.
A workaround is to set the `quarkus.servlet.context-path` in like this:
```
quarkus.servlet.context-path=${quarkus.http.root-path}
``` | non_priority | testhttpresource annotation injects endpoint url without the quarkus http root path segment describe the bug when injecting an endpoint url in test using the io quarkus test common http testhttpresource annotation the injected path does not contain a segment specified by the quarkus http root path config property expected behavior a full enpoint url with including the value of quarkus http root path should be injected actual behavior the injected url lacks the quarkus http root path segment how to reproduce testhttpendpoint myresource class testhttpresource url myresourceurl the injected url would lack the path segment set by the quarkus http root path property output of uname a or ver microsoft windows output of java version openjdk version graalvm version if different from java no response quarkus version or git rev final build tool ie output of mvnw version or gradlew version gradle additional information it seems that this happens because the class uses the test url config property to determine an endpoint url which is in turn is provided by the using the following expression as you can see instead of the quarkus http root path the quarkus servlet context path is used which is not applicable for a standalone application a workaround is to set the quarkus servlet context path in like this quarkus servlet context path quarkus http root path | 0 |
80,098 | 9,979,456,952 | IssuesEvent | 2019-07-09 22:57:41 | 18F/fs-open-forest-platform | https://api.github.com/repos/18F/fs-open-forest-platform | closed | Usability research for Special Use stories #627, 530, 531 | Design Special Uses | ## Notes
* What are things we should consider when making this story *
This story is for the purposes of capturing the work related to the usability research around the content flow for a special uses permit applicant.
## Acceptance Criteria
- [x] We have an understanding of what will work for a content strategy for these stories..
- [x] We know what changes (if any) we should make to the designs for the workflow and content of 627, 530 and 531
## Tasks
- [x] Recruit participants
- [x] Create research plan
- [x] Create usability script
- [x] Have the usability tests
- [x] Synthesis
- [x] PO approved
## Definition of Done
- [ ] Pull requests meet technical definition of done
- [ ] Compare finished design with mockup
- [ ] Usability tested
| 1.0 | Usability research for Special Use stories #627, 530, 531 - ## Notes
* What are things we should consider when making this story *
This story is for the purposes of capturing the work related to the usability research around the content flow for a special uses permit applicant.
## Acceptance Criteria
- [x] We have an understanding of what will work for a content strategy for these stories..
- [x] We know what changes (if any) we should make to the designs for the workflow and content of 627, 530 and 531
## Tasks
- [x] Recruit participants
- [x] Create research plan
- [x] Create usability script
- [x] Have the usability tests
- [x] Synthesis
- [x] PO approved
## Definition of Done
- [ ] Pull requests meet technical definition of done
- [ ] Compare finished design with mockup
- [ ] Usability tested
| non_priority | usability research for special use stories notes what are things we should consider when making this story this story is for the purposes of capturing the work related to the usability research around the content flow for a special uses permit applicant acceptance criteria we have an understanding of what will work for a content strategy for these stories we know what changes if any we should make to the designs for the workflow and content of and tasks recruit participants create research plan create usability script have the usability tests synthesis po approved definition of done pull requests meet technical definition of done compare finished design with mockup usability tested | 0 |
33,272 | 7,072,457,418 | IssuesEvent | 2018-01-09 00:40:14 | jccastillo0007/eFacturaT | https://api.github.com/repos/jccastillo0007/eFacturaT | opened | Navision 3.3 Producción - error en nota de crédito con documentos relacionados | bug defect | Te mandé un correo.
Creo que el problema es que en documentos relacionados, envías el folios interno en lugar del UUID. | 1.0 | Navision 3.3 Producción - error en nota de crédito con documentos relacionados - Te mandé un correo.
Creo que el problema es que en documentos relacionados, envías el folios interno en lugar del UUID. | non_priority | navision producción error en nota de crédito con documentos relacionados te mandé un correo creo que el problema es que en documentos relacionados envías el folios interno en lugar del uuid | 0 |
24,414 | 12,102,386,776 | IssuesEvent | 2020-04-20 16:36:50 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | closed | Auto Create COA Department Permits | Product: AMANDA Project: ATD AMANDA Backlog Service: Apps Service: Product Type: Enhancement Workgroup: ROW | Description: How can we streamline the ROW permitting for city departments? Goals include:
Create permit folders by importing data, versus requiring an application.
Upgrade the folder so it aligns with the actual processes taking place with COA ROW permits. (Take out extra infos, cut extra processes, update folder expiration rules, auto-issue permits.)
Request Date: 2019-03-14 14:43:00
Request ID: DTS19-104445
Status: Backlog
Customer Priority: 0
Level of Effort: Large Project
DTS URL: https://atd.knack.com/dts#service-requests/view-issue-details/5c8aaee1aacd0b52f0ffc744
*Migrated from [atd-amanda #58](https://github.com/cityofaustin/atd-amanda/issues/58)* | 2.0 | Auto Create COA Department Permits - Description: How can we streamline the ROW permitting for city departments? Goals include:
Create permit folders by importing data, versus requiring an application.
Upgrade the folder so it aligns with the actual processes taking place with COA ROW permits. (Take out extra infos, cut extra processes, update folder expiration rules, auto-issue permits.)
Request Date: 2019-03-14 14:43:00
Request ID: DTS19-104445
Status: Backlog
Customer Priority: 0
Level of Effort: Large Project
DTS URL: https://atd.knack.com/dts#service-requests/view-issue-details/5c8aaee1aacd0b52f0ffc744
*Migrated from [atd-amanda #58](https://github.com/cityofaustin/atd-amanda/issues/58)* | non_priority | auto create coa department permits description how can we streamline the row permitting for city departments goals include create permit folders by importing data versus requiring an application upgrade the folder so it aligns with the actual processes taking place with coa row permits take out extra infos cut extra processes update folder expiration rules auto issue permits request date request id status backlog customer priority level of effort large project dts url migrated from | 0 |
186,826 | 21,992,908,152 | IssuesEvent | 2022-05-26 01:09:53 | gmright-service-gmright/gmright2.github.io- | https://api.github.com/repos/gmright-service-gmright/gmright2.github.io- | opened | CVE-2022-29181 (High) detected in nokogiri-1.10.9.gem | security vulnerability | ## CVE-2022-29181 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nokogiri-1.10.9.gem</b></p></summary>
<p>Nokogiri (鋸) is an HTML, XML, SAX, and Reader parser. Among
Nokogiri's many features is the ability to search documents via XPath
or CSS3 selectors.</p>
<p>Library home page: <a href="https://rubygems.org/gems/nokogiri-1.10.9.gem">https://rubygems.org/gems/nokogiri-1.10.9.gem</a></p>
<p>Path to dependency file: /Gmright/Milestones/Gmright-market/Commerce/Net_holder/Blue-sky/Gemfile.lock</p>
<p>Path to vulnerable library: /var/lib/gems/2.5.0/cache/nokogiri-1.10.9.gem</p>
<p>
Dependency Hierarchy:
- github-pages-206.gem (Root Library)
- :x: **nokogiri-1.10.9.gem** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Nokogiri is an open source XML and HTML library for Ruby. Nokogiri prior to version 1.13.6 does not type-check all inputs into the XML and HTML4 SAX parsers, allowing specially crafted untrusted inputs to cause illegal memory access errors (segfault) or reads from unrelated memory. Version 1.13.6 contains a patch for this issue. As a workaround, ensure the untrusted input is a `String` by calling `#to_s` or equivalent.
<p>Publish Date: 2022-05-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29181>CVE-2022-29181</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29181">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29181</a></p>
<p>Release Date: 2022-05-20</p>
<p>Fix Resolution: nokogiri - 1.13.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-29181 (High) detected in nokogiri-1.10.9.gem - ## CVE-2022-29181 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nokogiri-1.10.9.gem</b></p></summary>
<p>Nokogiri (鋸) is an HTML, XML, SAX, and Reader parser. Among
Nokogiri's many features is the ability to search documents via XPath
or CSS3 selectors.</p>
<p>Library home page: <a href="https://rubygems.org/gems/nokogiri-1.10.9.gem">https://rubygems.org/gems/nokogiri-1.10.9.gem</a></p>
<p>Path to dependency file: /Gmright/Milestones/Gmright-market/Commerce/Net_holder/Blue-sky/Gemfile.lock</p>
<p>Path to vulnerable library: /var/lib/gems/2.5.0/cache/nokogiri-1.10.9.gem</p>
<p>
Dependency Hierarchy:
- github-pages-206.gem (Root Library)
- :x: **nokogiri-1.10.9.gem** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Nokogiri is an open source XML and HTML library for Ruby. Nokogiri prior to version 1.13.6 does not type-check all inputs into the XML and HTML4 SAX parsers, allowing specially crafted untrusted inputs to cause illegal memory access errors (segfault) or reads from unrelated memory. Version 1.13.6 contains a patch for this issue. As a workaround, ensure the untrusted input is a `String` by calling `#to_s` or equivalent.
<p>Publish Date: 2022-05-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29181>CVE-2022-29181</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29181">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29181</a></p>
<p>Release Date: 2022-05-20</p>
<p>Fix Resolution: nokogiri - 1.13.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in nokogiri gem cve high severity vulnerability vulnerable library nokogiri gem nokogiri 鋸 is an html xml sax and reader parser among nokogiri s many features is the ability to search documents via xpath or selectors library home page a href path to dependency file gmright milestones gmright market commerce net holder blue sky gemfile lock path to vulnerable library var lib gems cache nokogiri gem dependency hierarchy github pages gem root library x nokogiri gem vulnerable library found in base branch master vulnerability details nokogiri is an open source xml and html library for ruby nokogiri prior to version does not type check all inputs into the xml and sax parsers allowing specially crafted untrusted inputs to cause illegal memory access errors segfault or reads from unrelated memory version contains a patch for this issue as a workaround ensure the untrusted input is a string by calling to s or equivalent publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution nokogiri step up your open source security game with whitesource | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.