Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
173,072 | 14,401,179,932 | IssuesEvent | 2020-12-03 13:23:58 | alibaba/inclavare-containers | https://api.github.com/repos/alibaba/inclavare-containers | closed | Support k8s/pouch + pouchd + containerd + containerd-shim-rune-v2 + rune | documentation enhancement medium | Run through the whole link. | 1.0 | Support k8s/pouch + pouchd + containerd + containerd-shim-rune-v2 + rune - Run through the whole link. | non_priority | support pouch pouchd containerd containerd shim rune rune run through the whole link | 0 |
14,857 | 3,291,023,552 | IssuesEvent | 2015-10-30 05:19:51 | aspnet/Mvc | https://api.github.com/repos/aspnet/Mvc | closed | FormCollection always null | by design | This worked in Beta7. (Maybe this is a breaking change and the expected behavior?)
FormCollection is always null. Changing it to IFormCollection solves the problem.
```html
<form method="post" action="~/Start/FormTestPost">
<input type="hidden" name="test1" value="1" />
<input type="hidden" name="test2" value="2" />
<button class="btn btn-primary" type="submit">Post</button>
</form>
```
```csharp
public ActionResult FormTest()
{
return View();
}
[HttpPost]
public ActionResult FormTestPost(FormCollection form)
{
return RedirectToAction("FormTest");
}
``` | 1.0 | FormCollection always null - This worked in Beta7. (Maybe this is a breaking change and the expected behavior?)
FormCollection is always null. Changing it to IFormCollection solves the problem.
```html
<form method="post" action="~/Start/FormTestPost">
<input type="hidden" name="test1" value="1" />
<input type="hidden" name="test2" value="2" />
<button class="btn btn-primary" type="submit">Post</button>
</form>
```
```csharp
public ActionResult FormTest()
{
return View();
}
[HttpPost]
public ActionResult FormTestPost(FormCollection form)
{
return RedirectToAction("FormTest");
}
``` | non_priority | formcollection always null this worked in maybe this is a breaking change and the expected behavior formcollection is always null changing it to iformcollection solves the problem html post csharp public actionresult formtest return view public actionresult formtestpost formcollection form return redirecttoaction formtest | 0 |
5,132 | 2,762,112,575 | IssuesEvent | 2015-04-28 20:51:43 | rust-lang/rust | https://api.github.com/repos/rust-lang/rust | closed | Grammar tests | A-an-interesting-project A-grammar A-testsuite P-medium | It would be nice to have confidence about what sort of grammar Rust has. One possible way we could do that:
* Extract EBNF from the manual
* Use a script to convert it to whatever format antlr wants
* Run the entire test suite through the both the rustc parser and antlr parser. Where one fails so should the other. | 1.0 | Grammar tests - It would be nice to have confidence about what sort of grammar Rust has. One possible way we could do that:
* Extract EBNF from the manual
* Use a script to convert it to whatever format antlr wants
* Run the entire test suite through the both the rustc parser and antlr parser. Where one fails so should the other. | non_priority | grammar tests it would be nice to have confidence about what sort of grammar rust has one possible way we could do that extract ebnf from the manual use a script to convert it to whatever format antlr wants run the entire test suite through the both the rustc parser and antlr parser where one fails so should the other | 0 |
261,646 | 22,762,530,090 | IssuesEvent | 2022-07-07 22:52:34 | mozilla/tls-canary | https://api.github.com/repos/mozilla/tls-canary | closed | Linux test fail in OneCRL-Tools when run on travis | tests linux ARCHIVED | While we're away Travis has developed issues around running the OneCRL-Tools Go module.
This error is not reproducible in our Ubuntu-16-based EC2 environment which makes this rather hard to debug. Travis' Linux images are from the stone age (running Trusty with Go 1.7.4 after upgrading), so breakage may be related to that.
```
tests.zz_tlscanary_integration_test.test_tlscanary_regression_and_log
TLS Canary can make regression runs ... package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports bufio: unrecognized import path "bufio"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports bytes: unrecognized import path "bytes"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports crypto/x509/pkix: unrecognized import path "crypto/x509/pkix"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports encoding/asn1: unrecognized import path "encoding/asn1"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports encoding/base64: unrecognized import path "encoding/base64"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports encoding/hex: unrecognized import path "encoding/hex"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports encoding/json: unrecognized import path "encoding/json"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports errors: unrecognized import path "errors"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports flag: unrecognized import path "flag"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports fmt: unrecognized import path "fmt"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports runtime: unrecognized import path "runtime"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports sync: unrecognized import path "sync"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports syscall: unrecognized import path "syscall"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports unsafe: unrecognized import path "unsafe"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports io: unrecognized import path "io"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports unicode/utf8: unrecognized import path "unicode/utf8"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports encoding: unrecognized import path "encoding"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports math: unrecognized import path "math"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports os: unrecognized import path "os"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports reflect: unrecognized import path "reflect"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports regexp: unrecognized import path "regexp"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports sort: unrecognized import path "sort"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports strconv: unrecognized import path "strconv"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports strings: unrecognized import path "strings"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports time: unrecognized import path "time"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports unicode: unrecognized import path "unicode"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports io/ioutil: unrecognized import path "io/ioutil"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports github.com/mozilla/OneCRL-Tools/oneCRL
imports github.com/mozilla/OneCRL-Tools/util
imports net/http: unrecognized import path "net/http"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports github.com/mozilla/OneCRL-Tools/oneCRL
imports github.com/mozilla/OneCRL-Tools/util
imports net/url: unrecognized import path "net/url"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports github.com/mozilla/OneCRL-Tools/oneCRL
imports github.com/mozilla/OneCRL-Tools/util
imports log: unrecognized import path "log"
ERROR
tests.zz_tlscanary_integration_test.test_tlscanary_srcupdate_and_scan_and_log
TLS Canary can update source DBs ... package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports bufio: unrecognized import path "bufio"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports bytes: unrecognized import path "bytes"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports crypto/x509/pkix: unrecognized import path "crypto/x509/pkix"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports encoding: unrecognized import path "encoding"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports encoding/asn1: unrecognized import path "encoding/asn1"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports encoding/base64: unrecognized import path "encoding/base64"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports encoding/hex: unrecognized import path "encoding/hex"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports encoding/json: unrecognized import path "encoding/json"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports errors: unrecognized import path "errors"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports flag: unrecognized import path "flag"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports fmt: unrecognized import path "fmt"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports runtime: unrecognized import path "runtime"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports sync: unrecognized import path "sync"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports syscall: unrecognized import path "syscall"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports unsafe: unrecognized import path "unsafe"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports io: unrecognized import path "io"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports unicode/utf8: unrecognized import path "unicode/utf8"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports math: unrecognized import path "math"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports os: unrecognized import path "os"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports reflect: unrecognized import path "reflect"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports regexp: unrecognized import path "regexp"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports sort: unrecognized import path "sort"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports strconv: unrecognized import path "strconv"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports strings: unrecognized import path "strings"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports time: unrecognized import path "time"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports unicode: unrecognized import path "unicode"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports io/ioutil: unrecognized import path "io/ioutil"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports github.com/mozilla/OneCRL-Tools/oneCRL
imports github.com/mozilla/OneCRL-Tools/util
imports net/http: unrecognized import path "net/http"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports github.com/mozilla/OneCRL-Tools/oneCRL
imports github.com/mozilla/OneCRL-Tools/util
imports net/url: unrecognized import path "net/url"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports github.com/mozilla/OneCRL-Tools/oneCRL
imports github.com/mozilla/OneCRL-Tools/util
imports log: unrecognized import path "log"
ERROR
======================================================================
ERROR: tests.zz_tlscanary_integration_test.test_tlscanary_regression_and_log
TLS Canary can make regression runs
----------------------------------------------------------------------
Traceback (most recent call last):
File "/home/travis/build/mozilla/tls-canary/.eggs/nose-1.3.7-py2.7.egg/nose/case.py", line 197, in runTest
self.test(*self.arg)
File "/home/travis/build/mozilla/tls-canary/tests/zz_tlscanary_integration_test.py", line 29, in test_tlscanary_regression_and_log
ret = main.main(argv)
File "/home/travis/build/mozilla/tls-canary/tlscanary/main.py", line 200, in main
loader.run(args, module_dir, tmp_dir)
File "/home/travis/build/mozilla/tls-canary/tlscanary/loader.py", line 28, in run
current_mode.setup()
File "/home/travis/build/mozilla/tls-canary/tlscanary/modes/regression.py", line 103, in setup
self.test_profile = self.make_profile("test_profile", self.args.onecrl)
File "/home/travis/build/mozilla/tls-canary/tlscanary/modes/basemode.py", line 244, in make_profile
revocations_file = one_crl.get_list(one_crl_env, self.args.workdir, self.args.onecrlpin)
File "/home/travis/build/mozilla/tls-canary/tlscanary/one_crl_downloader.py", line 55, in get_list
sys.exit(5)
SystemExit: 5
-------------------- >> begin captured stdout << ---------------------
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/key4.db -> /tmp/tlscanary_WkLlB_/test_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/cert8.db -> /tmp/tlscanary_WkLlB_/test_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/SecurityPreloadState.txt -> /tmp/tlscanary_WkLlB_/test_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/pkcs11.txt -> /tmp/tlscanary_WkLlB_/test_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/cert9.db -> /tmp/tlscanary_WkLlB_/test_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/SiteSecurityServiceState.txt -> /tmp/tlscanary_WkLlB_/test_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/revocations.txt -> /tmp/tlscanary_WkLlB_/test_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/key3.db -> /tmp/tlscanary_WkLlB_/test_profile
--------------------- >> end captured stdout << ----------------------
======================================================================
ERROR: tests.zz_tlscanary_integration_test.test_tlscanary_srcupdate_and_scan_and_log
TLS Canary can update source DBs
----------------------------------------------------------------------
Traceback (most recent call last):
File "/home/travis/build/mozilla/tls-canary/.eggs/nose-1.3.7-py2.7.egg/nose/case.py", line 197, in runTest
self.test(*self.arg)
File "/home/travis/build/mozilla/tls-canary/tests/zz_tlscanary_integration_test.py", line 90, in test_tlscanary_srcupdate_and_scan_and_log
ret = main.main(argv)
File "/home/travis/build/mozilla/tls-canary/tlscanary/main.py", line 200, in main
loader.run(args, module_dir, tmp_dir)
File "/home/travis/build/mozilla/tls-canary/tlscanary/loader.py", line 28, in run
current_mode.setup()
File "/home/travis/build/mozilla/tls-canary/tlscanary/modes/sourceupdate.py", line 54, in setup
self.profile = self.make_profile("base_profile")
File "/home/travis/build/mozilla/tls-canary/tlscanary/modes/basemode.py", line 244, in make_profile
revocations_file = one_crl.get_list(one_crl_env, self.args.workdir, self.args.onecrlpin)
File "/home/travis/build/mozilla/tls-canary/tlscanary/one_crl_downloader.py", line 55, in get_list
sys.exit(5)
SystemExit: 5
-------------------- >> begin captured stdout << ---------------------
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/key4.db -> /tmp/tlscanary_rnSiBO/base_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/cert8.db -> /tmp/tlscanary_rnSiBO/base_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/SecurityPreloadState.txt -> /tmp/tlscanary_rnSiBO/base_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/pkcs11.txt -> /tmp/tlscanary_rnSiBO/base_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/cert9.db -> /tmp/tlscanary_rnSiBO/base_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/SiteSecurityServiceState.txt -> /tmp/tlscanary_rnSiBO/base_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/revocations.txt -> /tmp/tlscanary_rnSiBO/base_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/key3.db -> /tmp/tlscanary_rnSiBO/base_profile
--------------------- >> end captured stdout << ----------------------
----------------------------------------------------------------------
Ran 24 tests in 20.734s
FAILED (errors=2, skipped=1)
Test failed: <unittest.runner.TextTestResult run=24 errors=2 failures=0>
error: Test failed: <unittest.runner.TextTestResult run=24 errors=2 failures=0>
The command "python setup.py test" exited with 1.
Done. Your build exited with 1.
``` | 1.0 | Linux test fail in OneCRL-Tools when run on travis - While we're away Travis has developed issues around running the OneCRL-Tools Go module.
This error is not reproducible in our Ubuntu-16-based EC2 environment which makes this rather hard to debug. Travis' Linux images are from the stone age (running Trusty with Go 1.7.4 after upgrading), so breakage may be related to that.
```
tests.zz_tlscanary_integration_test.test_tlscanary_regression_and_log
TLS Canary can make regression runs ... package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports bufio: unrecognized import path "bufio"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports bytes: unrecognized import path "bytes"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports crypto/x509/pkix: unrecognized import path "crypto/x509/pkix"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports encoding/asn1: unrecognized import path "encoding/asn1"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports encoding/base64: unrecognized import path "encoding/base64"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports encoding/hex: unrecognized import path "encoding/hex"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports encoding/json: unrecognized import path "encoding/json"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports errors: unrecognized import path "errors"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports flag: unrecognized import path "flag"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports fmt: unrecognized import path "fmt"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports runtime: unrecognized import path "runtime"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports sync: unrecognized import path "sync"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports syscall: unrecognized import path "syscall"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports unsafe: unrecognized import path "unsafe"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports io: unrecognized import path "io"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports unicode/utf8: unrecognized import path "unicode/utf8"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports encoding: unrecognized import path "encoding"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports math: unrecognized import path "math"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports os: unrecognized import path "os"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports reflect: unrecognized import path "reflect"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports regexp: unrecognized import path "regexp"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports sort: unrecognized import path "sort"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports strconv: unrecognized import path "strconv"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports strings: unrecognized import path "strings"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports time: unrecognized import path "time"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports unicode: unrecognized import path "unicode"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports io/ioutil: unrecognized import path "io/ioutil"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports github.com/mozilla/OneCRL-Tools/oneCRL
imports github.com/mozilla/OneCRL-Tools/util
imports net/http: unrecognized import path "net/http"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports github.com/mozilla/OneCRL-Tools/oneCRL
imports github.com/mozilla/OneCRL-Tools/util
imports net/url: unrecognized import path "net/url"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports github.com/mozilla/OneCRL-Tools/oneCRL
imports github.com/mozilla/OneCRL-Tools/util
imports log: unrecognized import path "log"
ERROR
tests.zz_tlscanary_integration_test.test_tlscanary_srcupdate_and_scan_and_log
TLS Canary can update source DBs ... package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports bufio: unrecognized import path "bufio"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports bytes: unrecognized import path "bytes"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports crypto/x509/pkix: unrecognized import path "crypto/x509/pkix"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports encoding: unrecognized import path "encoding"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports encoding/asn1: unrecognized import path "encoding/asn1"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports encoding/base64: unrecognized import path "encoding/base64"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports encoding/hex: unrecognized import path "encoding/hex"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports encoding/json: unrecognized import path "encoding/json"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports errors: unrecognized import path "errors"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports flag: unrecognized import path "flag"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports fmt: unrecognized import path "fmt"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports runtime: unrecognized import path "runtime"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports sync: unrecognized import path "sync"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports syscall: unrecognized import path "syscall"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports unsafe: unrecognized import path "unsafe"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports io: unrecognized import path "io"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports unicode/utf8: unrecognized import path "unicode/utf8"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports math: unrecognized import path "math"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports os: unrecognized import path "os"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports reflect: unrecognized import path "reflect"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports regexp: unrecognized import path "regexp"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports sort: unrecognized import path "sort"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports strconv: unrecognized import path "strconv"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports strings: unrecognized import path "strings"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports time: unrecognized import path "time"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports unicode: unrecognized import path "unicode"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports io/ioutil: unrecognized import path "io/ioutil"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports github.com/mozilla/OneCRL-Tools/oneCRL
imports github.com/mozilla/OneCRL-Tools/util
imports net/http: unrecognized import path "net/http"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports github.com/mozilla/OneCRL-Tools/oneCRL
imports github.com/mozilla/OneCRL-Tools/util
imports net/url: unrecognized import path "net/url"
package github.com/mozilla/OneCRL-Tools/oneCRL2RevocationsTxt
imports github.com/mozilla/OneCRL-Tools/config
imports golang.org/x/crypto/ssh/terminal
imports golang.org/x/sys/unix
imports gopkg.in/yaml.v2
imports github.com/mozilla/OneCRL-Tools/oneCRL
imports github.com/mozilla/OneCRL-Tools/util
imports log: unrecognized import path "log"
ERROR
======================================================================
ERROR: tests.zz_tlscanary_integration_test.test_tlscanary_regression_and_log
TLS Canary can make regression runs
----------------------------------------------------------------------
Traceback (most recent call last):
File "/home/travis/build/mozilla/tls-canary/.eggs/nose-1.3.7-py2.7.egg/nose/case.py", line 197, in runTest
self.test(*self.arg)
File "/home/travis/build/mozilla/tls-canary/tests/zz_tlscanary_integration_test.py", line 29, in test_tlscanary_regression_and_log
ret = main.main(argv)
File "/home/travis/build/mozilla/tls-canary/tlscanary/main.py", line 200, in main
loader.run(args, module_dir, tmp_dir)
File "/home/travis/build/mozilla/tls-canary/tlscanary/loader.py", line 28, in run
current_mode.setup()
File "/home/travis/build/mozilla/tls-canary/tlscanary/modes/regression.py", line 103, in setup
self.test_profile = self.make_profile("test_profile", self.args.onecrl)
File "/home/travis/build/mozilla/tls-canary/tlscanary/modes/basemode.py", line 244, in make_profile
revocations_file = one_crl.get_list(one_crl_env, self.args.workdir, self.args.onecrlpin)
File "/home/travis/build/mozilla/tls-canary/tlscanary/one_crl_downloader.py", line 55, in get_list
sys.exit(5)
SystemExit: 5
-------------------- >> begin captured stdout << ---------------------
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/key4.db -> /tmp/tlscanary_WkLlB_/test_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/cert8.db -> /tmp/tlscanary_WkLlB_/test_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/SecurityPreloadState.txt -> /tmp/tlscanary_WkLlB_/test_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/pkcs11.txt -> /tmp/tlscanary_WkLlB_/test_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/cert9.db -> /tmp/tlscanary_WkLlB_/test_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/SiteSecurityServiceState.txt -> /tmp/tlscanary_WkLlB_/test_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/revocations.txt -> /tmp/tlscanary_WkLlB_/test_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/key3.db -> /tmp/tlscanary_WkLlB_/test_profile
--------------------- >> end captured stdout << ----------------------
======================================================================
ERROR: tests.zz_tlscanary_integration_test.test_tlscanary_srcupdate_and_scan_and_log
TLS Canary can update source DBs
----------------------------------------------------------------------
Traceback (most recent call last):
File "/home/travis/build/mozilla/tls-canary/.eggs/nose-1.3.7-py2.7.egg/nose/case.py", line 197, in runTest
self.test(*self.arg)
File "/home/travis/build/mozilla/tls-canary/tests/zz_tlscanary_integration_test.py", line 90, in test_tlscanary_srcupdate_and_scan_and_log
ret = main.main(argv)
File "/home/travis/build/mozilla/tls-canary/tlscanary/main.py", line 200, in main
loader.run(args, module_dir, tmp_dir)
File "/home/travis/build/mozilla/tls-canary/tlscanary/loader.py", line 28, in run
current_mode.setup()
File "/home/travis/build/mozilla/tls-canary/tlscanary/modes/sourceupdate.py", line 54, in setup
self.profile = self.make_profile("base_profile")
File "/home/travis/build/mozilla/tls-canary/tlscanary/modes/basemode.py", line 244, in make_profile
revocations_file = one_crl.get_list(one_crl_env, self.args.workdir, self.args.onecrlpin)
File "/home/travis/build/mozilla/tls-canary/tlscanary/one_crl_downloader.py", line 55, in get_list
sys.exit(5)
SystemExit: 5
-------------------- >> begin captured stdout << ---------------------
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/key4.db -> /tmp/tlscanary_rnSiBO/base_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/cert8.db -> /tmp/tlscanary_rnSiBO/base_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/SecurityPreloadState.txt -> /tmp/tlscanary_rnSiBO/base_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/pkcs11.txt -> /tmp/tlscanary_rnSiBO/base_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/cert9.db -> /tmp/tlscanary_rnSiBO/base_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/SiteSecurityServiceState.txt -> /tmp/tlscanary_rnSiBO/base_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/revocations.txt -> /tmp/tlscanary_rnSiBO/base_profile
copying /home/travis/build/mozilla/tls-canary/tlscanary/default_profile/key3.db -> /tmp/tlscanary_rnSiBO/base_profile
--------------------- >> end captured stdout << ----------------------
----------------------------------------------------------------------
Ran 24 tests in 20.734s
FAILED (errors=2, skipped=1)
Test failed: <unittest.runner.TextTestResult run=24 errors=2 failures=0>
error: Test failed: <unittest.runner.TextTestResult run=24 errors=2 failures=0>
The command "python setup.py test" exited with 1.
Done. Your build exited with 1.
``` | non_priority | linux test fail in onecrl tools when run on travis while we re away travis has developed issues around running the onecrl tools go module this error is not reproducible in our ubuntu based environment which makes this rather hard to debug travis linux images are from the stone age running trusty with go after upgrading so breakage may be related to that tests zz tlscanary integration test test tlscanary regression and log tls canary can make regression runs package github com mozilla onecrl tools imports bufio unrecognized import path bufio package github com mozilla onecrl tools imports bytes unrecognized import path bytes package github com mozilla onecrl tools imports crypto pkix unrecognized import path crypto pkix package github com mozilla onecrl tools imports encoding unrecognized import path encoding package github com mozilla onecrl tools imports encoding unrecognized import path encoding package github com mozilla onecrl tools imports encoding hex unrecognized import path encoding hex package github com mozilla onecrl tools imports encoding json unrecognized import path encoding json package github com mozilla onecrl tools imports errors unrecognized import path errors package github com mozilla onecrl tools imports flag unrecognized import path flag package github com mozilla onecrl tools imports fmt unrecognized import path fmt package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports runtime unrecognized import path runtime package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports sync unrecognized import path sync package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports syscall unrecognized import path syscall package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports unsafe unrecognized import path unsafe package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports io unrecognized import path io package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports unicode unrecognized import path unicode package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports encoding unrecognized import path encoding package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports math unrecognized import path math package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports os unrecognized import path os package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports reflect unrecognized import path reflect package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports regexp unrecognized import path regexp package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports sort unrecognized import path sort package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports strconv unrecognized import path strconv package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports strings unrecognized import path strings package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports time unrecognized import path time package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports unicode unrecognized import path unicode package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports io ioutil unrecognized import path io ioutil package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports github com mozilla onecrl tools onecrl imports github com mozilla onecrl tools util imports net http unrecognized import path net http package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports github com mozilla onecrl tools onecrl imports github com mozilla onecrl tools util imports net url unrecognized import path net url package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports github com mozilla onecrl tools onecrl imports github com mozilla onecrl tools util imports log unrecognized import path log error tests zz tlscanary integration test test tlscanary srcupdate and scan and log tls canary can update source dbs package github com mozilla onecrl tools imports bufio unrecognized import path bufio package github com mozilla onecrl tools imports bytes unrecognized import path bytes package github com mozilla onecrl tools imports crypto pkix unrecognized import path crypto pkix package github com mozilla onecrl tools imports encoding unrecognized import path encoding package github com mozilla onecrl tools imports encoding unrecognized import path encoding package github com mozilla onecrl tools imports encoding unrecognized import path encoding package github com mozilla onecrl tools imports encoding hex unrecognized import path encoding hex package github com mozilla onecrl tools imports encoding json unrecognized import path encoding json package github com mozilla onecrl tools imports errors unrecognized import path errors package github com mozilla onecrl tools imports flag unrecognized import path flag package github com mozilla onecrl tools imports fmt unrecognized import path fmt package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports runtime unrecognized import path runtime package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports sync unrecognized import path sync package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports syscall unrecognized import path syscall package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports unsafe unrecognized import path unsafe package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports io unrecognized import path io package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports unicode unrecognized import path unicode package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports math unrecognized import path math package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports os unrecognized import path os package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports reflect unrecognized import path reflect package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports regexp unrecognized import path regexp package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports sort unrecognized import path sort package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports strconv unrecognized import path strconv package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports strings unrecognized import path strings package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports time unrecognized import path time package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports unicode unrecognized import path unicode package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports io ioutil unrecognized import path io ioutil package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports github com mozilla onecrl tools onecrl imports github com mozilla onecrl tools util imports net http unrecognized import path net http package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports github com mozilla onecrl tools onecrl imports github com mozilla onecrl tools util imports net url unrecognized import path net url package github com mozilla onecrl tools imports github com mozilla onecrl tools config imports golang org x crypto ssh terminal imports golang org x sys unix imports gopkg in yaml imports github com mozilla onecrl tools onecrl imports github com mozilla onecrl tools util imports log unrecognized import path log error error tests zz tlscanary integration test test tlscanary regression and log tls canary can make regression runs traceback most recent call last file home travis build mozilla tls canary eggs nose egg nose case py line in runtest self test self arg file home travis build mozilla tls canary tests zz tlscanary integration test py line in test tlscanary regression and log ret main main argv file home travis build mozilla tls canary tlscanary main py line in main loader run args module dir tmp dir file home travis build mozilla tls canary tlscanary loader py line in run current mode setup file home travis build mozilla tls canary tlscanary modes regression py line in setup self test profile self make profile test profile self args onecrl file home travis build mozilla tls canary tlscanary modes basemode py line in make profile revocations file one crl get list one crl env self args workdir self args onecrlpin file home travis build mozilla tls canary tlscanary one crl downloader py line in get list sys exit systemexit begin captured stdout copying home travis build mozilla tls canary tlscanary default profile db tmp tlscanary wkllb test profile copying home travis build mozilla tls canary tlscanary default profile db tmp tlscanary wkllb test profile copying home travis build mozilla tls canary tlscanary default profile securitypreloadstate txt tmp tlscanary wkllb test profile copying home travis build mozilla tls canary tlscanary default profile txt tmp tlscanary wkllb test profile copying home travis build mozilla tls canary tlscanary default profile db tmp tlscanary wkllb test profile copying home travis build mozilla tls canary tlscanary default profile sitesecurityservicestate txt tmp tlscanary wkllb test profile copying home travis build mozilla tls canary tlscanary default profile revocations txt tmp tlscanary wkllb test profile copying home travis build mozilla tls canary tlscanary default profile db tmp tlscanary wkllb test profile end captured stdout error tests zz tlscanary integration test test tlscanary srcupdate and scan and log tls canary can update source dbs traceback most recent call last file home travis build mozilla tls canary eggs nose egg nose case py line in runtest self test self arg file home travis build mozilla tls canary tests zz tlscanary integration test py line in test tlscanary srcupdate and scan and log ret main main argv file home travis build mozilla tls canary tlscanary main py line in main loader run args module dir tmp dir file home travis build mozilla tls canary tlscanary loader py line in run current mode setup file home travis build mozilla tls canary tlscanary modes sourceupdate py line in setup self profile self make profile base profile file home travis build mozilla tls canary tlscanary modes basemode py line in make profile revocations file one crl get list one crl env self args workdir self args onecrlpin file home travis build mozilla tls canary tlscanary one crl downloader py line in get list sys exit systemexit begin captured stdout copying home travis build mozilla tls canary tlscanary default profile db tmp tlscanary rnsibo base profile copying home travis build mozilla tls canary tlscanary default profile db tmp tlscanary rnsibo base profile copying home travis build mozilla tls canary tlscanary default profile securitypreloadstate txt tmp tlscanary rnsibo base profile copying home travis build mozilla tls canary tlscanary default profile txt tmp tlscanary rnsibo base profile copying home travis build mozilla tls canary tlscanary default profile db tmp tlscanary rnsibo base profile copying home travis build mozilla tls canary tlscanary default profile sitesecurityservicestate txt tmp tlscanary rnsibo base profile copying home travis build mozilla tls canary tlscanary default profile revocations txt tmp tlscanary rnsibo base profile copying home travis build mozilla tls canary tlscanary default profile db tmp tlscanary rnsibo base profile end captured stdout ran tests in failed errors skipped test failed error test failed the command python setup py test exited with done your build exited with | 0 |
286,118 | 31,239,972,610 | IssuesEvent | 2023-08-20 18:45:39 | samq-ghdemo/railsgoat | https://api.github.com/repos/samq-ghdemo/railsgoat | opened | puma-6.0.2.gem: 1 vulnerabilities (highest severity is: 7.3) | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>puma-6.0.2.gem</b></p></summary>
<p>Puma is a simple, fast, threaded, and highly parallel HTTP 1.1 server for Ruby/Rack applications. Puma is intended for use in both development and production environments. It's great for highly parallel Ruby implementations such as Rubinius and JRuby as well as as providing process worker support to support CRuby well.</p>
<p>Library home page: <a href="https://rubygems.org/gems/puma-6.0.2.gem">https://rubygems.org/gems/puma-6.0.2.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/puma-6.0.2.gem</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/railsgoat/commit/933dc816d15b994acb05d0e6e19bb566f8e0d1a8">933dc816d15b994acb05d0e6e19bb566f8e0d1a8</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (puma version) | Remediation Possible** |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2023-40175](https://www.mend.io/vulnerability-database/CVE-2023-40175) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.3 | puma-6.0.2.gem | Direct | puma - 5.6.7,6.3.1 | ✅ |
<p>**In some cases, Remediation PR cannot be created automatically for a vulnerability despite the availability of remediation</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2023-40175</summary>
### Vulnerable Library - <b>puma-6.0.2.gem</b></p>
<p>Puma is a simple, fast, threaded, and highly parallel HTTP 1.1 server for Ruby/Rack applications. Puma is intended for use in both development and production environments. It's great for highly parallel Ruby implementations such as Rubinius and JRuby as well as as providing process worker support to support CRuby well.</p>
<p>Library home page: <a href="https://rubygems.org/gems/puma-6.0.2.gem">https://rubygems.org/gems/puma-6.0.2.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/puma-6.0.2.gem</p>
<p>
Dependency Hierarchy:
- :x: **puma-6.0.2.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/railsgoat/commit/933dc816d15b994acb05d0e6e19bb566f8e0d1a8">933dc816d15b994acb05d0e6e19bb566f8e0d1a8</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Puma is a Ruby/Rack web server built for parallelism. Prior to versions 6.3.1 and 5.6.7, puma exhibited incorrect behavior when parsing chunked transfer encoding bodies and zero-length Content-Length headers in a way that allowed HTTP request smuggling. Severity of this issue is highly dependent on the nature of the web site using puma is. This could be caused by either incorrect parsing of trailing fields in chunked transfer encoding bodies or by parsing of blank/zero-length Content-Length headers. Both issues have been addressed and this vulnerability has been fixed in versions 6.3.1 and 5.6.7. Users are advised to upgrade. There are no known workarounds for this vulnerability.
<p>Publish Date: 2023-08-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-40175>CVE-2023-40175</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2023-40175">https://www.cve.org/CVERecord?id=CVE-2023-40175</a></p>
<p>Release Date: 2023-08-18</p>
<p>Fix Resolution: puma - 5.6.7,6.3.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation will be attempted for this issue.
</details>
***
<p>:rescue_worker_helmet:Automatic Remediation will be attempted for this issue.</p> | True | puma-6.0.2.gem: 1 vulnerabilities (highest severity is: 7.3) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>puma-6.0.2.gem</b></p></summary>
<p>Puma is a simple, fast, threaded, and highly parallel HTTP 1.1 server for Ruby/Rack applications. Puma is intended for use in both development and production environments. It's great for highly parallel Ruby implementations such as Rubinius and JRuby as well as as providing process worker support to support CRuby well.</p>
<p>Library home page: <a href="https://rubygems.org/gems/puma-6.0.2.gem">https://rubygems.org/gems/puma-6.0.2.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/puma-6.0.2.gem</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/railsgoat/commit/933dc816d15b994acb05d0e6e19bb566f8e0d1a8">933dc816d15b994acb05d0e6e19bb566f8e0d1a8</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (puma version) | Remediation Possible** |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2023-40175](https://www.mend.io/vulnerability-database/CVE-2023-40175) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.3 | puma-6.0.2.gem | Direct | puma - 5.6.7,6.3.1 | ✅ |
<p>**In some cases, Remediation PR cannot be created automatically for a vulnerability despite the availability of remediation</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2023-40175</summary>
### Vulnerable Library - <b>puma-6.0.2.gem</b></p>
<p>Puma is a simple, fast, threaded, and highly parallel HTTP 1.1 server for Ruby/Rack applications. Puma is intended for use in both development and production environments. It's great for highly parallel Ruby implementations such as Rubinius and JRuby as well as as providing process worker support to support CRuby well.</p>
<p>Library home page: <a href="https://rubygems.org/gems/puma-6.0.2.gem">https://rubygems.org/gems/puma-6.0.2.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/puma-6.0.2.gem</p>
<p>
Dependency Hierarchy:
- :x: **puma-6.0.2.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/railsgoat/commit/933dc816d15b994acb05d0e6e19bb566f8e0d1a8">933dc816d15b994acb05d0e6e19bb566f8e0d1a8</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Puma is a Ruby/Rack web server built for parallelism. Prior to versions 6.3.1 and 5.6.7, puma exhibited incorrect behavior when parsing chunked transfer encoding bodies and zero-length Content-Length headers in a way that allowed HTTP request smuggling. Severity of this issue is highly dependent on the nature of the web site using puma is. This could be caused by either incorrect parsing of trailing fields in chunked transfer encoding bodies or by parsing of blank/zero-length Content-Length headers. Both issues have been addressed and this vulnerability has been fixed in versions 6.3.1 and 5.6.7. Users are advised to upgrade. There are no known workarounds for this vulnerability.
<p>Publish Date: 2023-08-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-40175>CVE-2023-40175</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2023-40175">https://www.cve.org/CVERecord?id=CVE-2023-40175</a></p>
<p>Release Date: 2023-08-18</p>
<p>Fix Resolution: puma - 5.6.7,6.3.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation will be attempted for this issue.
</details>
***
<p>:rescue_worker_helmet:Automatic Remediation will be attempted for this issue.</p> | non_priority | puma gem vulnerabilities highest severity is vulnerable library puma gem puma is a simple fast threaded and highly parallel http server for ruby rack applications puma is intended for use in both development and production environments it s great for highly parallel ruby implementations such as rubinius and jruby as well as as providing process worker support to support cruby well library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache puma gem found in head commit a href vulnerabilities cve severity cvss dependency type fixed in puma version remediation possible high puma gem direct puma in some cases remediation pr cannot be created automatically for a vulnerability despite the availability of remediation details cve vulnerable library puma gem puma is a simple fast threaded and highly parallel http server for ruby rack applications puma is intended for use in both development and production environments it s great for highly parallel ruby implementations such as rubinius and jruby as well as as providing process worker support to support cruby well library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache puma gem dependency hierarchy x puma gem vulnerable library found in head commit a href found in base branch master vulnerability details puma is a ruby rack web server built for parallelism prior to versions and puma exhibited incorrect behavior when parsing chunked transfer encoding bodies and zero length content length headers in a way that allowed http request smuggling severity of this issue is highly dependent on the nature of the web site using puma is this could be caused by either incorrect parsing of trailing fields in chunked transfer encoding bodies or by parsing of blank zero length content length headers both issues have been addressed and this vulnerability has been fixed in versions and users are advised to upgrade there are no known workarounds for this vulnerability publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution puma rescue worker helmet automatic remediation will be attempted for this issue rescue worker helmet automatic remediation will be attempted for this issue | 0 |
9,029 | 12,533,485,804 | IssuesEvent | 2020-06-04 17:41:18 | trussworks/react-uswds | https://api.github.com/repos/trussworks/react-uswds | closed | Investigate loki and other visual regression testing tools for storybook | status: needs requirements type: feature | As part of automated testing, I recommend we set up https://loki.js.org/ to run against storybook in this project, and the corresponding CircleCI job to run it so that contributions and improvements do not break the visual appearance of components unexpected. | 1.0 | Investigate loki and other visual regression testing tools for storybook - As part of automated testing, I recommend we set up https://loki.js.org/ to run against storybook in this project, and the corresponding CircleCI job to run it so that contributions and improvements do not break the visual appearance of components unexpected. | non_priority | investigate loki and other visual regression testing tools for storybook as part of automated testing i recommend we set up to run against storybook in this project and the corresponding circleci job to run it so that contributions and improvements do not break the visual appearance of components unexpected | 0 |
179,990 | 21,606,828,233 | IssuesEvent | 2022-05-04 04:59:15 | jamandujanoa/WASA | https://api.github.com/repos/jamandujanoa/WASA | opened | Implement security playbooks for incident response | WARP-Import WAF-Assessment Security Operational Procedures Incident Response | <a href="https://docs.microsoft.com/azure/security-center/workflow-automation">Implement security playbooks for incident response</a>
<p><b>Why Consider This?</b></p>
Playbooks ensure security process steps are done quickly, consistently, and according to your predefined requirements. Incident responders are part of a central SecOps team and need to understand security insights for an application. Playbooks can help to understand the security concepts and cover typical investigation activities and parameters. It is recommended to automate as many steps as you can, as automation reduces overhead.
<p><b>Context</b></p>
<p><b>Suggested Actions</b></p>
<p><span>Automate threat response with playbooks (Microsoft Sentinel) or automated workflows (Microsoft Defender for Cloud) to respond to security incicdents</span></p>
<p><b>Learn More</b></p>
<p><a href="https://docs.microsoft.com/en-us/azure/defender-for-cloud/workflow-automation" target="_blank"><span>https://docs.microsoft.com/en-us/azure/defender-for-cloud/workflow-automation</span></a><span /></p><p><a href="https://docs.microsoft.com/en-us/azure/sentinel/automate-responses-with-playbooks" target="_blank"><span>Automate threat response with playbooks in Microsoft Sentinel</span></a><span /></p> | True | Implement security playbooks for incident response - <a href="https://docs.microsoft.com/azure/security-center/workflow-automation">Implement security playbooks for incident response</a>
<p><b>Why Consider This?</b></p>
Playbooks ensure security process steps are done quickly, consistently, and according to your predefined requirements. Incident responders are part of a central SecOps team and need to understand security insights for an application. Playbooks can help to understand the security concepts and cover typical investigation activities and parameters. It is recommended to automate as many steps as you can, as automation reduces overhead.
<p><b>Context</b></p>
<p><b>Suggested Actions</b></p>
<p><span>Automate threat response with playbooks (Microsoft Sentinel) or automated workflows (Microsoft Defender for Cloud) to respond to security incicdents</span></p>
<p><b>Learn More</b></p>
<p><a href="https://docs.microsoft.com/en-us/azure/defender-for-cloud/workflow-automation" target="_blank"><span>https://docs.microsoft.com/en-us/azure/defender-for-cloud/workflow-automation</span></a><span /></p><p><a href="https://docs.microsoft.com/en-us/azure/sentinel/automate-responses-with-playbooks" target="_blank"><span>Automate threat response with playbooks in Microsoft Sentinel</span></a><span /></p> | non_priority | implement security playbooks for incident response why consider this playbooks ensure security process steps are done quickly consistently and according to your predefined requirements incident responders are part of a central secops team and need to understand security insights for an application playbooks can help to understand the security concepts and cover typical investigation activities and parameters it is recommended to automate as many steps as you can as automation reduces overhead context suggested actions automate threat response with playbooks microsoft sentinel or automated workflows microsoft defender for cloud to respond to security incicdents learn more automate threat response with playbooks in microsoft sentinel | 0 |
134,491 | 18,471,326,454 | IssuesEvent | 2021-10-17 19:44:03 | samq-ghdemo/Java-Demo | https://api.github.com/repos/samq-ghdemo/Java-Demo | opened | CVE-2019-17571 (High) detected in log4j-1.2.13.jar | security vulnerability | ## CVE-2019-17571 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-1.2.13.jar</b></p></summary>
<p>Log4j</p>
<p>Library home page: <a href="http://logging.apache.org/log4j/">http://logging.apache.org/log4j/</a></p>
<p>Path to dependency file: Java-Demo/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/log4j/log4j/1.2.13/log4j-1.2.13.jar</p>
<p>
Dependency Hierarchy:
- slf4j-log4j12-1.5.0.jar (Root Library)
- :x: **log4j-1.2.13.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Java-Demo/commit/3ac002d655870dcf124820ae1a9cd2e7e9121da6">3ac002d655870dcf124820ae1a9cd2e7e9121da6</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Included in Log4j 1.2 is a SocketServer class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data. This affects Log4j versions up to 1.2 up to 1.2.17.
<p>Publish Date: 2019-12-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17571>CVE-2019-17571</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17571">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17571</a></p>
<p>Release Date: 2019-12-20</p>
<p>Fix Resolution: org.apache.logging.log4j:log4j-core:2.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"log4j","packageName":"log4j","packageVersion":"1.2.13","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.slf4j:slf4j-log4j12:1.5.0;log4j:log4j:1.2.13","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.logging.log4j:log4j-core:2.0"}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-17571","vulnerabilityDetails":"Included in Log4j 1.2 is a SocketServer class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data. This affects Log4j versions up to 1.2 up to 1.2.17.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17571","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2019-17571 (High) detected in log4j-1.2.13.jar - ## CVE-2019-17571 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-1.2.13.jar</b></p></summary>
<p>Log4j</p>
<p>Library home page: <a href="http://logging.apache.org/log4j/">http://logging.apache.org/log4j/</a></p>
<p>Path to dependency file: Java-Demo/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/log4j/log4j/1.2.13/log4j-1.2.13.jar</p>
<p>
Dependency Hierarchy:
- slf4j-log4j12-1.5.0.jar (Root Library)
- :x: **log4j-1.2.13.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Java-Demo/commit/3ac002d655870dcf124820ae1a9cd2e7e9121da6">3ac002d655870dcf124820ae1a9cd2e7e9121da6</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Included in Log4j 1.2 is a SocketServer class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data. This affects Log4j versions up to 1.2 up to 1.2.17.
<p>Publish Date: 2019-12-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17571>CVE-2019-17571</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17571">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17571</a></p>
<p>Release Date: 2019-12-20</p>
<p>Fix Resolution: org.apache.logging.log4j:log4j-core:2.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"log4j","packageName":"log4j","packageVersion":"1.2.13","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.slf4j:slf4j-log4j12:1.5.0;log4j:log4j:1.2.13","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.logging.log4j:log4j-core:2.0"}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-17571","vulnerabilityDetails":"Included in Log4j 1.2 is a SocketServer class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data. This affects Log4j versions up to 1.2 up to 1.2.17.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17571","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in jar cve high severity vulnerability vulnerable library jar library home page a href path to dependency file java demo pom xml path to vulnerable library home wss scanner repository jar dependency hierarchy jar root library x jar vulnerable library found in head commit a href found in base branch main vulnerability details included in is a socketserver class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data this affects versions up to up to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache logging core isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org isminimumfixversionavailable true minimumfixversion org apache logging core basebranches vulnerabilityidentifier cve vulnerabilitydetails included in is a socketserver class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data this affects versions up to up to vulnerabilityurl | 0 |
53,391 | 11,046,882,341 | IssuesEvent | 2019-12-09 17:45:24 | cclagodna/goblins-stole-my-bike | https://api.github.com/repos/cclagodna/goblins-stole-my-bike | opened | FINAL CODE 12.09.19 | code | [12.09.19.zip](https://github.com/cclagodna/goblins-stole-my-bike/files/3941012/12.09.19.zip)
Here's the final game code.
I had to fill in some monster designs, so there a few new monsters. They are using some names and stats defined by Abdul. | 1.0 | FINAL CODE 12.09.19 - [12.09.19.zip](https://github.com/cclagodna/goblins-stole-my-bike/files/3941012/12.09.19.zip)
Here's the final game code.
I had to fill in some monster designs, so there a few new monsters. They are using some names and stats defined by Abdul. | non_priority | final code here s the final game code i had to fill in some monster designs so there a few new monsters they are using some names and stats defined by abdul | 0 |
65,115 | 19,099,518,847 | IssuesEvent | 2021-11-29 20:38:47 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | opened | Thread summary ignores text decorations | T-Defect | ### Steps to reproduce

### Outcome
#### What did you expect?
not everything is needed, but decorations like ~~strikethrough~~ change the meaning and should be reflected
#### What happened instead?
Looks to me like it's filtered similarly or the same way previews in the room list are.



### Operating system
w10
### Application version
Element version: 1.9.5 Olm version: 3.2.3
### How did you install the app?
element.io
### Homeserver
_No response_
### Will you send logs?
No | 1.0 | Thread summary ignores text decorations - ### Steps to reproduce

### Outcome
#### What did you expect?
not everything is needed, but decorations like ~~strikethrough~~ change the meaning and should be reflected
#### What happened instead?
Looks to me like it's filtered similarly or the same way previews in the room list are.



### Operating system
w10
### Application version
Element version: 1.9.5 Olm version: 3.2.3
### How did you install the app?
element.io
### Homeserver
_No response_
### Will you send logs?
No | non_priority | thread summary ignores text decorations steps to reproduce outcome what did you expect not everything is needed but decorations like strikethrough change the meaning and should be reflected what happened instead looks to me like it s filtered similarly or the same way previews in the room list are operating system application version element version olm version how did you install the app element io homeserver no response will you send logs no | 0 |
17,316 | 3,604,551,536 | IssuesEvent | 2016-02-03 23:21:10 | UCHIC/ODM2Sensor | https://api.github.com/repos/UCHIC/ODM2Sensor | closed | Nested Entry in 'Create Equipment' | django version enhancement ready for testing | On the Create Equipment page, we should implement the ability to create an equipment model.

| 1.0 | Nested Entry in 'Create Equipment' - On the Create Equipment page, we should implement the ability to create an equipment model.

| non_priority | nested entry in create equipment on the create equipment page we should implement the ability to create an equipment model | 0 |
76,022 | 9,374,777,073 | IssuesEvent | 2019-04-04 00:53:49 | aws/aws-toolkit-vscode | https://api.github.com/repos/aws/aws-toolkit-vscode | opened | Edit Lambda Configurations | category:feature-request needs-design | As a user, I can see and modify configuration details of a Lambda function without having to use the web console.
The aspects that can be modified are currently TBD/open for requests. | 1.0 | Edit Lambda Configurations - As a user, I can see and modify configuration details of a Lambda function without having to use the web console.
The aspects that can be modified are currently TBD/open for requests. | non_priority | edit lambda configurations as a user i can see and modify configuration details of a lambda function without having to use the web console the aspects that can be modified are currently tbd open for requests | 0 |
30,039 | 13,196,965,679 | IssuesEvent | 2020-08-13 21:48:50 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | When i try and run the command to get the certificate expiration i get an error that base64 command is not recognized | Pri2 container-service/svc | base64 : The term 'base64' is not recognized as the name of a cmdlet, function, script file, or operable program.
Check the spelling of the name, or if a path was included, verify that the path is correct and try again.
At line:1 char:119
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 9b78509d-73eb-6c32-aee1-9b34685a64ff
* Version Independent ID: 6f87cf70-1f5a-0f9e-862d-ae1436595f3b
* Content: [Rotate certificates in Azure Kubernetes Service (AKS) - Azure Kubernetes Service](https://docs.microsoft.com/en-us/azure/aks/certificate-rotation)
* Content Source: [articles/aks/certificate-rotation.md](https://github.com/MicrosoftDocs/azure-docs/blob/master/articles/aks/certificate-rotation.md)
* Service: **container-service**
* GitHub Login: @mlearned
* Microsoft Alias: **mlearned** | 1.0 | When i try and run the command to get the certificate expiration i get an error that base64 command is not recognized - base64 : The term 'base64' is not recognized as the name of a cmdlet, function, script file, or operable program.
Check the spelling of the name, or if a path was included, verify that the path is correct and try again.
At line:1 char:119
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 9b78509d-73eb-6c32-aee1-9b34685a64ff
* Version Independent ID: 6f87cf70-1f5a-0f9e-862d-ae1436595f3b
* Content: [Rotate certificates in Azure Kubernetes Service (AKS) - Azure Kubernetes Service](https://docs.microsoft.com/en-us/azure/aks/certificate-rotation)
* Content Source: [articles/aks/certificate-rotation.md](https://github.com/MicrosoftDocs/azure-docs/blob/master/articles/aks/certificate-rotation.md)
* Service: **container-service**
* GitHub Login: @mlearned
* Microsoft Alias: **mlearned** | non_priority | when i try and run the command to get the certificate expiration i get an error that command is not recognized the term is not recognized as the name of a cmdlet function script file or operable program check the spelling of the name or if a path was included verify that the path is correct and try again at line char document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service container service github login mlearned microsoft alias mlearned | 0 |
93,301 | 10,764,659,471 | IssuesEvent | 2019-11-01 08:57:09 | ChengGeng97/ped | https://api.github.com/repos/ChengGeng97/ped | opened | UG says that attendance can be undone | severity.Low type.DocumentationBug | Documentation of undo command lists attendance as undo-able, despite it not being a state-changing command and thus not undo-able.
| 1.0 | UG says that attendance can be undone - Documentation of undo command lists attendance as undo-able, despite it not being a state-changing command and thus not undo-able.
| non_priority | ug says that attendance can be undone documentation of undo command lists attendance as undo able despite it not being a state changing command and thus not undo able | 0 |
39,988 | 10,431,117,117 | IssuesEvent | 2019-09-17 08:25:47 | virtualsatellite/VirtualSatellite4-Core | https://api.github.com/repos/virtualsatellite/VirtualSatellite4-Core | opened | Travis-Ci fails on downloading overtarget dependencies | bug build | Travis fails to download the dependencies for overtarget. The connection to sourceforge runs into a timeout.
It is suggested to use 'travis_retry' for the curl. | 1.0 | Travis-Ci fails on downloading overtarget dependencies - Travis fails to download the dependencies for overtarget. The connection to sourceforge runs into a timeout.
It is suggested to use 'travis_retry' for the curl. | non_priority | travis ci fails on downloading overtarget dependencies travis fails to download the dependencies for overtarget the connection to sourceforge runs into a timeout it is suggested to use travis retry for the curl | 0 |
44,733 | 13,078,751,612 | IssuesEvent | 2020-08-01 00:34:52 | spawaskar-cora/cora-docs | https://api.github.com/repos/spawaskar-cora/cora-docs | opened | Update scripts/style to latest releases | enhancement security | Update scripts/style to latest releases, these include the following
- [ ] jQuery
- [ ] Bootstrap
- [ ] Font Awesome | True | Update scripts/style to latest releases - Update scripts/style to latest releases, these include the following
- [ ] jQuery
- [ ] Bootstrap
- [ ] Font Awesome | non_priority | update scripts style to latest releases update scripts style to latest releases these include the following jquery bootstrap font awesome | 0 |
1,173 | 2,533,106,614 | IssuesEvent | 2015-01-23 20:45:41 | galenframework/galen | https://api.github.com/repos/galenframework/galen | closed | Test retry handler | c2 enhancement p3 ready for test | It would be nice to have a test retry mechanism like in TestNG. This will be applied on the JavaScript tests and in Standard test suite. Requirements still need to be clarified. Could be something like this.
```
testRetry(function (test, retryCount) {
if (retryCount > 2) {
return false;
}
else return true;
});
```
It should also produce only the reports of the last retry of a test so that we don't get all the original failed reports. And also the retry should kick in only in case the test run was failed | 1.0 | Test retry handler - It would be nice to have a test retry mechanism like in TestNG. This will be applied on the JavaScript tests and in Standard test suite. Requirements still need to be clarified. Could be something like this.
```
testRetry(function (test, retryCount) {
if (retryCount > 2) {
return false;
}
else return true;
});
```
It should also produce only the reports of the last retry of a test so that we don't get all the original failed reports. And also the retry should kick in only in case the test run was failed | non_priority | test retry handler it would be nice to have a test retry mechanism like in testng this will be applied on the javascript tests and in standard test suite requirements still need to be clarified could be something like this testretry function test retrycount if retrycount return false else return true it should also produce only the reports of the last retry of a test so that we don t get all the original failed reports and also the retry should kick in only in case the test run was failed | 0 |
123,527 | 16,507,252,016 | IssuesEvent | 2021-05-25 20:59:36 | keep-network/keep-core | https://api.github.com/repos/keep-network/keep-core | closed | How to Stake section on the Keep website | :old_key: token dashboard 🎨 design in progress | A how to stake section on the Keep website that include:
- information about the liquidity pools
- information about keep only pool
| 1.0 | How to Stake section on the Keep website - A how to stake section on the Keep website that include:
- information about the liquidity pools
- information about keep only pool
| non_priority | how to stake section on the keep website a how to stake section on the keep website that include information about the liquidity pools information about keep only pool | 0 |
75,657 | 20,924,342,511 | IssuesEvent | 2022-03-24 20:47:25 | pyqg/pyqg | https://api.github.com/repos/pyqg/pyqg | closed | build issue on os x | building | On yosemite 10.10.5, xcode version 6.4, I get the following error when I try to build with clang
``` bash
$ python setup.py build_ext --inplace
```
or gcc
``` bash
$ CC=/usr/local/gcc-4.8/bin/gcc python setup.py build_ext --inplace --library-dirs=/usr/local/gcc-4.8/lib
```
```
ld: library not found for -lgcc_s.10.5
```
It sounds similar to [this issue](http://alexnj.com/blog/library-not-found-for-lgcc_s-10-5/).
| 1.0 | build issue on os x - On yosemite 10.10.5, xcode version 6.4, I get the following error when I try to build with clang
``` bash
$ python setup.py build_ext --inplace
```
or gcc
``` bash
$ CC=/usr/local/gcc-4.8/bin/gcc python setup.py build_ext --inplace --library-dirs=/usr/local/gcc-4.8/lib
```
```
ld: library not found for -lgcc_s.10.5
```
It sounds similar to [this issue](http://alexnj.com/blog/library-not-found-for-lgcc_s-10-5/).
| non_priority | build issue on os x on yosemite xcode version i get the following error when i try to build with clang bash python setup py build ext inplace or gcc bash cc usr local gcc bin gcc python setup py build ext inplace library dirs usr local gcc lib ld library not found for lgcc s it sounds similar to | 0 |
233,874 | 25,780,403,022 | IssuesEvent | 2022-12-09 15:26:54 | smb-h/Estates-price-prediction | https://api.github.com/repos/smb-h/Estates-price-prediction | closed | CVE-2022-35959 (High) detected in tensorflow-2.6.3-cp37-cp37m-manylinux2010_x86_64.whl | security vulnerability | ## CVE-2022-35959 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-2.6.3-cp37-cp37m-manylinux2010_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/73/a3/142f73d0e076f5582fd8da29c68af0413bf529933eed09f86a8857fab0d6/tensorflow-2.6.3-cp37-cp37m-manylinux2010_x86_64.whl">https://files.pythonhosted.org/packages/73/a3/142f73d0e076f5582fd8da29c68af0413bf529933eed09f86a8857fab0d6/tensorflow-2.6.3-cp37-cp37m-manylinux2010_x86_64.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-2.6.3-cp37-cp37m-manylinux2010_x86_64.whl** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an open source platform for machine learning. The implementation of `AvgPool3DGradOp` does not fully validate the input `orig_input_shape`. This results in an overflow that results in a `CHECK` failure which can be used to trigger a denial of service attack. We have patched the issue in GitHub commit 9178ac9d6389bdc54638ab913ea0e419234d14eb. The fix will be included in TensorFlow 2.10.0. We will also cherrypick this commit on TensorFlow 2.9.1, TensorFlow 2.8.1, and TensorFlow 2.7.2, as these are also affected and still in supported range. There are no known workarounds for this issue.
<p>Publish Date: 2022-09-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-35959>CVE-2022-35959</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-wxjj-cgcx-r3vq">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-wxjj-cgcx-r3vq</a></p>
<p>Release Date: 2022-09-16</p>
<p>Fix Resolution: tensorflow - 2.7.2,2.8.1,2.9.1,2.10.0, tensorflow-cpu - 2.7.2,2.8.1,2.9.1,2.10.0, tensorflow-gpu - 2.7.2,2.8.1,2.9.1,2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-35959 (High) detected in tensorflow-2.6.3-cp37-cp37m-manylinux2010_x86_64.whl - ## CVE-2022-35959 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-2.6.3-cp37-cp37m-manylinux2010_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/73/a3/142f73d0e076f5582fd8da29c68af0413bf529933eed09f86a8857fab0d6/tensorflow-2.6.3-cp37-cp37m-manylinux2010_x86_64.whl">https://files.pythonhosted.org/packages/73/a3/142f73d0e076f5582fd8da29c68af0413bf529933eed09f86a8857fab0d6/tensorflow-2.6.3-cp37-cp37m-manylinux2010_x86_64.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-2.6.3-cp37-cp37m-manylinux2010_x86_64.whl** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an open source platform for machine learning. The implementation of `AvgPool3DGradOp` does not fully validate the input `orig_input_shape`. This results in an overflow that results in a `CHECK` failure which can be used to trigger a denial of service attack. We have patched the issue in GitHub commit 9178ac9d6389bdc54638ab913ea0e419234d14eb. The fix will be included in TensorFlow 2.10.0. We will also cherrypick this commit on TensorFlow 2.9.1, TensorFlow 2.8.1, and TensorFlow 2.7.2, as these are also affected and still in supported range. There are no known workarounds for this issue.
<p>Publish Date: 2022-09-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-35959>CVE-2022-35959</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-wxjj-cgcx-r3vq">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-wxjj-cgcx-r3vq</a></p>
<p>Release Date: 2022-09-16</p>
<p>Fix Resolution: tensorflow - 2.7.2,2.8.1,2.9.1,2.10.0, tensorflow-cpu - 2.7.2,2.8.1,2.9.1,2.10.0, tensorflow-gpu - 2.7.2,2.8.1,2.9.1,2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in tensorflow whl cve high severity vulnerability vulnerable library tensorflow whl tensorflow is an open source machine learning framework for everyone library home page a href path to dependency file requirements txt path to vulnerable library requirements txt dependency hierarchy x tensorflow whl vulnerable library found in base branch main vulnerability details tensorflow is an open source platform for machine learning the implementation of does not fully validate the input orig input shape this results in an overflow that results in a check failure which can be used to trigger a denial of service attack we have patched the issue in github commit the fix will be included in tensorflow we will also cherrypick this commit on tensorflow tensorflow and tensorflow as these are also affected and still in supported range there are no known workarounds for this issue publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tensorflow tensorflow cpu tensorflow gpu step up your open source security game with mend | 0 |
15,216 | 5,909,630,159 | IssuesEvent | 2017-05-20 01:38:23 | easywebhub/training-tasks | https://api.github.com/repos/easywebhub/training-tasks | opened | Nội dung trao đổi về easyweb sáng 20/05/17 | EasyBuilder enhancement |
### Nội dung
- chia sẻ về các nguyên tắc làm việc, trao đổi trực tiếp của team, [chi-tiet](https://github.com/easywebhub/tasks/blob/master/README.md)
- 5 nguyên tắc làm việc
- cách trao đổi trực tiếp, gián tiếp hiệu quả
- nội dung cho training, xem các file .md trong https://github.com/easywebhub/trainning-tasks
- | 1.0 | Nội dung trao đổi về easyweb sáng 20/05/17 -
### Nội dung
- chia sẻ về các nguyên tắc làm việc, trao đổi trực tiếp của team, [chi-tiet](https://github.com/easywebhub/tasks/blob/master/README.md)
- 5 nguyên tắc làm việc
- cách trao đổi trực tiếp, gián tiếp hiệu quả
- nội dung cho training, xem các file .md trong https://github.com/easywebhub/trainning-tasks
- | non_priority | nội dung trao đổi về easyweb sáng nội dung chia sẻ về các nguyên tắc làm việc trao đổi trực tiếp của team nguyên tắc làm việc cách trao đổi trực tiếp gián tiếp hiệu quả nội dung cho training xem các file md trong | 0 |
1,091 | 3,031,124,648 | IssuesEvent | 2015-08-04 21:03:34 | hypery2k/owncloud | https://api.github.com/repos/hypery2k/owncloud | closed | wrong package | bug infrastructure roundcube | On this site
https://apps.owncloud.com/content/show.php/roundcube?content=151523
it is possible to download a package with the name 151523-roundcube_v2.6.1_build429.zip.
But if you have a look on roundcube/appinfo/version you can see: 2.5.4.
This is a old version where I have login problems.
Can you give me please the right package with the content of 2.6.1?
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/24212769-wrong-package?utm_campaign=plugin&utm_content=tracker%2F308690&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F308690&utm_medium=issues&utm_source=github).
</bountysource-plugin> | 1.0 | wrong package - On this site
https://apps.owncloud.com/content/show.php/roundcube?content=151523
it is possible to download a package with the name 151523-roundcube_v2.6.1_build429.zip.
But if you have a look on roundcube/appinfo/version you can see: 2.5.4.
This is a old version where I have login problems.
Can you give me please the right package with the content of 2.6.1?
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/24212769-wrong-package?utm_campaign=plugin&utm_content=tracker%2F308690&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F308690&utm_medium=issues&utm_source=github).
</bountysource-plugin> | non_priority | wrong package on this site it is possible to download a package with the name roundcube zip but if you have a look on roundcube appinfo version you can see this is a old version where i have login problems can you give me please the right package with the content of want to back this issue we accept bounties via | 0 |
337,508 | 30,248,896,362 | IssuesEvent | 2023-07-06 18:46:50 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | reopened | Fix jax_nn_activations.test_jax_nn_relu | JAX Frontend Sub Task Failing Test | | | |
|---|---|
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5387024906/jobs/9777788802"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5387024906/jobs/9777788802"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5387024906/jobs/9777788802"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5387024906/jobs/9777788802"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5478319447"><img src=https://img.shields.io/badge/-failure-red></a>
| 1.0 | Fix jax_nn_activations.test_jax_nn_relu - | | |
|---|---|
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5387024906/jobs/9777788802"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5387024906/jobs/9777788802"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5387024906/jobs/9777788802"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5387024906/jobs/9777788802"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5478319447"><img src=https://img.shields.io/badge/-failure-red></a>
| non_priority | fix jax nn activations test jax nn relu jax a href src numpy a href src tensorflow a href src torch a href src paddle a href src | 0 |
35,329 | 6,444,734,078 | IssuesEvent | 2017-08-12 16:19:57 | mangapress/mangapress | https://api.github.com/repos/mangapress/mangapress | opened | Documentation Updates | documentation | * [ ] Add "How to Extend Manga+Press" section to docs.manga-press.com
- Focus on the Manga+Press specific templates and how to override them
* [ ] Add new actions and filters to Manga+Press API documentation (developers.manga-press.com)
additional details to follow | 1.0 | Documentation Updates - * [ ] Add "How to Extend Manga+Press" section to docs.manga-press.com
- Focus on the Manga+Press specific templates and how to override them
* [ ] Add new actions and filters to Manga+Press API documentation (developers.manga-press.com)
additional details to follow | non_priority | documentation updates add how to extend manga press section to docs manga press com focus on the manga press specific templates and how to override them add new actions and filters to manga press api documentation developers manga press com additional details to follow | 0 |
186,338 | 15,055,147,281 | IssuesEvent | 2021-02-03 18:22:55 | biothings/biothings_explorer | https://api.github.com/repos/biothings/biothings_explorer | closed | Project Description Missing From PYPI landing page for BTE | documentation | BTE PYPI landing page: https://pypi.org/project/biothings-explorer/
The Project Description is currently empty. Need to point it to the README.md file of this repo.
Instructions: https://packaging.python.org/guides/making-a-pypi-friendly-readme/ | 1.0 | Project Description Missing From PYPI landing page for BTE - BTE PYPI landing page: https://pypi.org/project/biothings-explorer/
The Project Description is currently empty. Need to point it to the README.md file of this repo.
Instructions: https://packaging.python.org/guides/making-a-pypi-friendly-readme/ | non_priority | project description missing from pypi landing page for bte bte pypi landing page the project description is currently empty need to point it to the readme md file of this repo instructions | 0 |
130,974 | 10,676,926,164 | IssuesEvent | 2019-10-21 14:36:31 | imixs/imixs-workflow | https://api.github.com/repos/imixs/imixs-workflow | closed | ConfigService - support deprecated imixs.properties | feature testing | The ConfigService should provide a mechanism to support deprecated imixs.properties like:
lucence.fulltextFieldList -> index.fields
This allows a soft migration of properties in an application even if the old property is still used | 1.0 | ConfigService - support deprecated imixs.properties - The ConfigService should provide a mechanism to support deprecated imixs.properties like:
lucence.fulltextFieldList -> index.fields
This allows a soft migration of properties in an application even if the old property is still used | non_priority | configservice support deprecated imixs properties the configservice should provide a mechanism to support deprecated imixs properties like lucence fulltextfieldlist index fields this allows a soft migration of properties in an application even if the old property is still used | 0 |
4,641 | 2,868,900,868 | IssuesEvent | 2015-06-05 21:49:56 | wet-boew/wet-boew | https://api.github.com/repos/wet-boew/wet-boew | closed | Documentation Template for Tombstone Data | Content: Documentation | To help documenting the components of the Toolkit, please fill out the template below with the relevant information. Add the completed template as a comment on this issue.
### Component name
* The name of the component.
### Purpose
* A brief description of the component.
### Use when
* The instances when the use of the component is recommended or acceptable.
### Do not use when
* The instances when use of the component should be avoided or is discouraged.
### Working example
* A link to the working example of the component.
### HTML markup to enable the component in a Web page
* The base HTML markup to use to enable the component in a Web page.
### Configuration options
* The configuration options for the component.
### Source code
* A link to the folder containing the files for the component in the GitHub repository.
| 1.0 | Documentation Template for Tombstone Data - To help documenting the components of the Toolkit, please fill out the template below with the relevant information. Add the completed template as a comment on this issue.
### Component name
* The name of the component.
### Purpose
* A brief description of the component.
### Use when
* The instances when the use of the component is recommended or acceptable.
### Do not use when
* The instances when use of the component should be avoided or is discouraged.
### Working example
* A link to the working example of the component.
### HTML markup to enable the component in a Web page
* The base HTML markup to use to enable the component in a Web page.
### Configuration options
* The configuration options for the component.
### Source code
* A link to the folder containing the files for the component in the GitHub repository.
| non_priority | documentation template for tombstone data to help documenting the components of the toolkit please fill out the template below with the relevant information add the completed template as a comment on this issue component name the name of the component purpose a brief description of the component use when the instances when the use of the component is recommended or acceptable do not use when the instances when use of the component should be avoided or is discouraged working example a link to the working example of the component html markup to enable the component in a web page the base html markup to use to enable the component in a web page configuration options the configuration options for the component source code a link to the folder containing the files for the component in the github repository | 0 |
1,108 | 27,007,323,257 | IssuesEvent | 2023-02-10 12:46:59 | culturesofknowledge/emlo-project | https://api.github.com/repos/culturesofknowledge/emlo-project | closed | Same form is used for people and organisations | people form need more details | @anusharanganathan yes, same form used for people and organisation, but there have some difference between organisation and people | 1.0 | Same form is used for people and organisations - @anusharanganathan yes, same form used for people and organisation, but there have some difference between organisation and people | non_priority | same form is used for people and organisations anusharanganathan yes same form used for people and organisation but there have some difference between organisation and people | 0 |
24,187 | 12,234,632,260 | IssuesEvent | 2020-05-04 13:43:43 | mozilla-mobile/fenix | https://api.github.com/repos/mozilla-mobile/fenix | closed | Investigate if there are deps/assets we can leave uncompressed to improve performance | eng:performance needs:triage | In https://github.com/mozilla-mobile/fenix/pull/9363/, we identified that compressing `omni.ja` slows down performance. What other dependencies/assets might we leave uncompressed to improve performance?
@snorp Do you have any ideas? | True | Investigate if there are deps/assets we can leave uncompressed to improve performance - In https://github.com/mozilla-mobile/fenix/pull/9363/, we identified that compressing `omni.ja` slows down performance. What other dependencies/assets might we leave uncompressed to improve performance?
@snorp Do you have any ideas? | non_priority | investigate if there are deps assets we can leave uncompressed to improve performance in we identified that compressing omni ja slows down performance what other dependencies assets might we leave uncompressed to improve performance snorp do you have any ideas | 0 |
206,134 | 23,365,746,747 | IssuesEvent | 2022-08-10 15:13:23 | pactflow/example-bi-directional-consumer-nock | https://api.github.com/repos/pactflow/example-bi-directional-consumer-nock | opened | CVE-2022-0691 (High) detected in url-parse-1.4.7.tgz | security vulnerability | ## CVE-2022-0691 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.4.7.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.3.tgz (Root Library)
- webpack-dev-server-3.11.0.tgz
- sockjs-client-1.4.0.tgz
- :x: **url-parse-1.4.7.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/pactflow/example-bi-directional-consumer-nock/commit/aac7a171164d371bfa2840858243ccc5becb42c2">aac7a171164d371bfa2840858243ccc5becb42c2</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Authorization Bypass Through User-Controlled Key in NPM url-parse prior to 1.5.9.
<p>Publish Date: 2022-02-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0691>CVE-2022-0691</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0691">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0691</a></p>
<p>Release Date: 2022-02-21</p>
<p>Fix Resolution (url-parse): 1.5.9</p>
<p>Direct dependency fix Resolution (react-scripts): 3.4.4</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| True | CVE-2022-0691 (High) detected in url-parse-1.4.7.tgz - ## CVE-2022-0691 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.4.7.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.3.tgz (Root Library)
- webpack-dev-server-3.11.0.tgz
- sockjs-client-1.4.0.tgz
- :x: **url-parse-1.4.7.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/pactflow/example-bi-directional-consumer-nock/commit/aac7a171164d371bfa2840858243ccc5becb42c2">aac7a171164d371bfa2840858243ccc5becb42c2</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Authorization Bypass Through User-Controlled Key in NPM url-parse prior to 1.5.9.
<p>Publish Date: 2022-02-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0691>CVE-2022-0691</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0691">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0691</a></p>
<p>Release Date: 2022-02-21</p>
<p>Fix Resolution (url-parse): 1.5.9</p>
<p>Direct dependency fix Resolution (react-scripts): 3.4.4</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| non_priority | cve high detected in url parse tgz cve high severity vulnerability vulnerable library url parse tgz small footprint url parser that works seamlessly across node js and browser environments library home page a href path to dependency file package json path to vulnerable library node modules url parse package json dependency hierarchy react scripts tgz root library webpack dev server tgz sockjs client tgz x url parse tgz vulnerable library found in head commit a href found in base branch master vulnerability details authorization bypass through user controlled key in npm url parse prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution url parse direct dependency fix resolution react scripts check this box to open an automated fix pr | 0 |
181,387 | 21,658,650,411 | IssuesEvent | 2022-05-06 16:37:03 | yaeljacobs67/npm-plugin | https://api.github.com/repos/yaeljacobs67/npm-plugin | opened | CVE-2022-29167 (High) detected in hawk-7.0.7.tgz | security vulnerability | ## CVE-2022-29167 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>hawk-7.0.7.tgz</b></p></summary>
<p>HTTP Hawk Authentication Scheme</p>
<p>Library home page: <a href="https://registry.npmjs.org/hawk/-/hawk-7.0.7.tgz">https://registry.npmjs.org/hawk/-/hawk-7.0.7.tgz</a></p>
<p>Path to dependency file: /npm-plugin/package.json</p>
<p>Path to vulnerable library: /node_modules/hawk/package.json</p>
<p>
Dependency Hierarchy:
- :x: **hawk-7.0.7.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Hawk is an HTTP authentication scheme providing mechanisms for making authenticated HTTP requests with partial cryptographic verification of the request and response, covering the HTTP method, request URI, host, and optionally the request payload. Hawk used a regular expression to parse `Host` HTTP header (`Hawk.utils.parseHost()`), which was subject to regular expression DoS attack - meaning each added character in the attacker's input increases the computation time exponentially. `parseHost()` was patched in `9.0.1` to use built-in `URL` class to parse hostname instead. `Hawk.authenticate()` accepts `options` argument. If that contains `host` and `port`, those would be used instead of a call to `utils.parseHost()`.
<p>Publish Date: 2022-05-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29167>CVE-2022-29167</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mozilla/hawk/security/advisories/GHSA-44pw-h2cw-w3vq">https://github.com/mozilla/hawk/security/advisories/GHSA-44pw-h2cw-w3vq</a></p>
<p>Release Date: 2022-05-05</p>
<p>Fix Resolution: hawk - 9.0.1</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"hawk","packageVersion":"7.0.7","packageFilePaths":["/npm-plugin/package.json"],"isTransitiveDependency":false,"dependencyTree":"hawk:7.0.7","isMinimumFixVersionAvailable":true,"minimumFixVersion":"hawk - 9.0.1","isBinary":false}],"baseBranches":[],"vulnerabilityIdentifier":"CVE-2022-29167","vulnerabilityDetails":"Hawk is an HTTP authentication scheme providing mechanisms for making authenticated HTTP requests with partial cryptographic verification of the request and response, covering the HTTP method, request URI, host, and optionally the request payload. Hawk used a regular expression to parse `Host` HTTP header (`Hawk.utils.parseHost()`), which was subject to regular expression DoS attack - meaning each added character in the attacker\u0027s input increases the computation time exponentially. `parseHost()` was patched in `9.0.1` to use built-in `URL` class to parse hostname instead. `Hawk.authenticate()` accepts `options` argument. If that contains `host` and `port`, those would be used instead of a call to `utils.parseHost()`.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29167","cvss3Severity":"high","cvss3Score":"7.4","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Changed","C":"None","UI":"Required","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2022-29167 (High) detected in hawk-7.0.7.tgz - ## CVE-2022-29167 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>hawk-7.0.7.tgz</b></p></summary>
<p>HTTP Hawk Authentication Scheme</p>
<p>Library home page: <a href="https://registry.npmjs.org/hawk/-/hawk-7.0.7.tgz">https://registry.npmjs.org/hawk/-/hawk-7.0.7.tgz</a></p>
<p>Path to dependency file: /npm-plugin/package.json</p>
<p>Path to vulnerable library: /node_modules/hawk/package.json</p>
<p>
Dependency Hierarchy:
- :x: **hawk-7.0.7.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Hawk is an HTTP authentication scheme providing mechanisms for making authenticated HTTP requests with partial cryptographic verification of the request and response, covering the HTTP method, request URI, host, and optionally the request payload. Hawk used a regular expression to parse `Host` HTTP header (`Hawk.utils.parseHost()`), which was subject to regular expression DoS attack - meaning each added character in the attacker's input increases the computation time exponentially. `parseHost()` was patched in `9.0.1` to use built-in `URL` class to parse hostname instead. `Hawk.authenticate()` accepts `options` argument. If that contains `host` and `port`, those would be used instead of a call to `utils.parseHost()`.
<p>Publish Date: 2022-05-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29167>CVE-2022-29167</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mozilla/hawk/security/advisories/GHSA-44pw-h2cw-w3vq">https://github.com/mozilla/hawk/security/advisories/GHSA-44pw-h2cw-w3vq</a></p>
<p>Release Date: 2022-05-05</p>
<p>Fix Resolution: hawk - 9.0.1</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"hawk","packageVersion":"7.0.7","packageFilePaths":["/npm-plugin/package.json"],"isTransitiveDependency":false,"dependencyTree":"hawk:7.0.7","isMinimumFixVersionAvailable":true,"minimumFixVersion":"hawk - 9.0.1","isBinary":false}],"baseBranches":[],"vulnerabilityIdentifier":"CVE-2022-29167","vulnerabilityDetails":"Hawk is an HTTP authentication scheme providing mechanisms for making authenticated HTTP requests with partial cryptographic verification of the request and response, covering the HTTP method, request URI, host, and optionally the request payload. Hawk used a regular expression to parse `Host` HTTP header (`Hawk.utils.parseHost()`), which was subject to regular expression DoS attack - meaning each added character in the attacker\u0027s input increases the computation time exponentially. `parseHost()` was patched in `9.0.1` to use built-in `URL` class to parse hostname instead. `Hawk.authenticate()` accepts `options` argument. If that contains `host` and `port`, those would be used instead of a call to `utils.parseHost()`.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29167","cvss3Severity":"high","cvss3Score":"7.4","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Changed","C":"None","UI":"Required","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in hawk tgz cve high severity vulnerability vulnerable library hawk tgz http hawk authentication scheme library home page a href path to dependency file npm plugin package json path to vulnerable library node modules hawk package json dependency hierarchy x hawk tgz vulnerable library vulnerability details hawk is an http authentication scheme providing mechanisms for making authenticated http requests with partial cryptographic verification of the request and response covering the http method request uri host and optionally the request payload hawk used a regular expression to parse host http header hawk utils parsehost which was subject to regular expression dos attack meaning each added character in the attacker s input increases the computation time exponentially parsehost was patched in to use built in url class to parse hostname instead hawk authenticate accepts options argument if that contains host and port those would be used instead of a call to utils parsehost publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution hawk check this box to open an automated fix pr isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree hawk isminimumfixversionavailable true minimumfixversion hawk isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails hawk is an http authentication scheme providing mechanisms for making authenticated http requests with partial cryptographic verification of the request and response covering the http method request uri host and optionally the request payload hawk used a regular expression to parse host http header hawk utils parsehost which was subject to regular expression dos attack meaning each added character in the attacker input increases the computation time exponentially parsehost was patched in to use built in url class to parse hostname instead hawk authenticate accepts options argument if that contains host and port those would be used instead of a call to utils parsehost vulnerabilityurl | 0 |
237,710 | 19,667,831,278 | IssuesEvent | 2022-01-11 01:38:45 | dapr/cli | https://api.github.com/repos/dapr/cli | closed | Add unit test for run, uninstall, kubernetes in k8s package | area/test area/cli stale | ## Describe the proposal
Add unit test for run, uninstall, kubernetes in k8s package
part of #486
Follow pattern similar to https://github.com/dapr/cli/blob/master/pkg/kubernetes/client.go, https://github.com/dapr/cli/blob/master/pkg/kubernetes/status.go and https://github.com/dapr/cli/blob/master/pkg/kubernetes/status_test.go
## Release Note
<!-- How should the fix for this issue be communicated in our release notes? It can be populated later. -->
<!-- Keep it as a single line. Examples: -->
<!-- RELEASE NOTE: **ADD** New feature in Dapr. -->
<!-- RELEASE NOTE: **FIX** Bug in runtime. -->
<!-- RELEASE NOTE: **UPDATE** Runtime dependency. -->
RELEASE NOTE:
| 1.0 | Add unit test for run, uninstall, kubernetes in k8s package - ## Describe the proposal
Add unit test for run, uninstall, kubernetes in k8s package
part of #486
Follow pattern similar to https://github.com/dapr/cli/blob/master/pkg/kubernetes/client.go, https://github.com/dapr/cli/blob/master/pkg/kubernetes/status.go and https://github.com/dapr/cli/blob/master/pkg/kubernetes/status_test.go
## Release Note
<!-- How should the fix for this issue be communicated in our release notes? It can be populated later. -->
<!-- Keep it as a single line. Examples: -->
<!-- RELEASE NOTE: **ADD** New feature in Dapr. -->
<!-- RELEASE NOTE: **FIX** Bug in runtime. -->
<!-- RELEASE NOTE: **UPDATE** Runtime dependency. -->
RELEASE NOTE:
| non_priority | add unit test for run uninstall kubernetes in package describe the proposal add unit test for run uninstall kubernetes in package part of follow pattern similar to and release note release note | 0 |
47,252 | 13,056,080,589 | IssuesEvent | 2020-07-30 03:35:54 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | closed | GCDDispatch or I3Db still caching C frames across run changes (Trac #220) | I3Db Migrated from Trac defect | At run change, D (detector status), C (calibration) and G(geometry) should be
flushed and refetched from DB in the GCDDispatch process.
This definitely works ok for D frames, but C frames are not properly
requeried.
Right now, work arround to restart GCDDispatch process after loading new domcal.
G frames may have same issues.
This could be an issue for I3Db.
Migrated from https://code.icecube.wisc.edu/ticket/220
```json
{
"status": "closed",
"changetime": "2012-07-04T09:30:22",
"description": "At run change, D (detector status), C (calibration) and G(geometry) should be\nflushed and refetched from DB in the GCDDispatch process. \n\nThis definitely works ok for D frames, but C frames are not properly\nrequeried. \n\nRight now, work arround to restart GCDDispatch process after loading new domcal.\n\nG frames may have same issues.\n\nThis could be an issue for I3Db.",
"reporter": "blaufuss",
"cc": "",
"resolution": "fixed",
"_ts": "1341394222000000",
"component": "I3Db",
"summary": "GCDDispatch or I3Db still caching C frames across run changes",
"priority": "normal",
"keywords": "",
"time": "2010-12-01T16:35:31",
"milestone": "",
"owner": "kohnen",
"type": "defect"
}
```
| 1.0 | GCDDispatch or I3Db still caching C frames across run changes (Trac #220) - At run change, D (detector status), C (calibration) and G(geometry) should be
flushed and refetched from DB in the GCDDispatch process.
This definitely works ok for D frames, but C frames are not properly
requeried.
Right now, work arround to restart GCDDispatch process after loading new domcal.
G frames may have same issues.
This could be an issue for I3Db.
Migrated from https://code.icecube.wisc.edu/ticket/220
```json
{
"status": "closed",
"changetime": "2012-07-04T09:30:22",
"description": "At run change, D (detector status), C (calibration) and G(geometry) should be\nflushed and refetched from DB in the GCDDispatch process. \n\nThis definitely works ok for D frames, but C frames are not properly\nrequeried. \n\nRight now, work arround to restart GCDDispatch process after loading new domcal.\n\nG frames may have same issues.\n\nThis could be an issue for I3Db.",
"reporter": "blaufuss",
"cc": "",
"resolution": "fixed",
"_ts": "1341394222000000",
"component": "I3Db",
"summary": "GCDDispatch or I3Db still caching C frames across run changes",
"priority": "normal",
"keywords": "",
"time": "2010-12-01T16:35:31",
"milestone": "",
"owner": "kohnen",
"type": "defect"
}
```
| non_priority | gcddispatch or still caching c frames across run changes trac at run change d detector status c calibration and g geometry should be flushed and refetched from db in the gcddispatch process this definitely works ok for d frames but c frames are not properly requeried right now work arround to restart gcddispatch process after loading new domcal g frames may have same issues this could be an issue for migrated from json status closed changetime description at run change d detector status c calibration and g geometry should be nflushed and refetched from db in the gcddispatch process n nthis definitely works ok for d frames but c frames are not properly nrequeried n nright now work arround to restart gcddispatch process after loading new domcal n ng frames may have same issues n nthis could be an issue for reporter blaufuss cc resolution fixed ts component summary gcddispatch or still caching c frames across run changes priority normal keywords time milestone owner kohnen type defect | 0 |
380,910 | 26,434,649,878 | IssuesEvent | 2023-01-15 08:17:56 | keep-starknet-strange/beerus | https://api.github.com/repos/keep-starknet-strange/beerus | closed | Setup integration testing infrastructure | documentation enhancement test stale | ## Description
Setup an infrastructure for integration testing.
Should include:
- CI
- deployment scripts
- integrations tests | 1.0 | Setup integration testing infrastructure - ## Description
Setup an infrastructure for integration testing.
Should include:
- CI
- deployment scripts
- integrations tests | non_priority | setup integration testing infrastructure description setup an infrastructure for integration testing should include ci deployment scripts integrations tests | 0 |
38,102 | 15,503,479,342 | IssuesEvent | 2021-03-11 13:12:15 | kiiiyo/kiiiyo.io | https://api.github.com/repos/kiiiyo/kiiiyo.io | closed | 管理画面の開発環境を構築 | Feature Service | # Overview
管理画面の開発環境を構築する
## TODOs
- [x] Amplify dev環境に環境変数を設定する
- [x] Amplify yamlでCI/CD環境の対応をする | 1.0 | 管理画面の開発環境を構築 - # Overview
管理画面の開発環境を構築する
## TODOs
- [x] Amplify dev環境に環境変数を設定する
- [x] Amplify yamlでCI/CD環境の対応をする | non_priority | 管理画面の開発環境を構築 overview 管理画面の開発環境を構築する todos amplify dev環境に環境変数を設定する amplify yamlでci cd環境の対応をする | 0 |
433,405 | 30,326,408,384 | IssuesEvent | 2023-07-11 00:38:23 | privy-open-source/design-system | https://api.github.com/repos/privy-open-source/design-system | closed | Dropdown: Create dropdown header | documentation components |
- update docs style guide
- create dropdown header component | 1.0 | Dropdown: Create dropdown header -
- update docs style guide
- create dropdown header component | non_priority | dropdown create dropdown header update docs style guide create dropdown header component | 0 |
64,510 | 15,896,497,500 | IssuesEvent | 2021-04-11 17:38:32 | haskell/text | https://api.github.com/repos/haskell/text | closed | Can't build benchmarks | build failure | When trying to build benchmarks, I get a linker error, as the `cbits.c` from the `text` i have installed clash with the `cbits.c` from the `text` source code i'm currently working on and which i'm trying to benchmark.
```
Linking dist/build/text-benchmarks/text-benchmarks ...
/home/kuko/.cabal/lib/x86_64-linux-ghc-8.0.2/text-1.2.2.2-KC7dWoG09dA1F6jKj5GSqh/libHStext-1.2.2.2-KC7dWoG09dA1F6jKj5GSqh.a(cbits.o): In function `_hs_text_memcmp':
(.text+0x20): multiple definition of `_hs_text_memcmp'
dist/build/text-benchmarks/text-benchmarks-tmp/../cbits/cbits.o:cbits.c:(.text+0x0): first defined here
/home/kuko/.cabal/lib/x86_64-linux-ghc-8.0.2/text-1.2.2.2-KC7dWoG09dA1F6jKj5GSqh/libHStext-1.2.2.2-KC7dWoG09dA1F6jKj5GSqh.a(cbits.o): In function `_hs_text_decode_utf8_state':
(.text+0xe0): multiple definition of `_hs_text_decode_utf8_state'
dist/build/text-benchmarks/text-benchmarks-tmp/../cbits/cbits.o:cbits.c:(.text+0x20): first defined here
/home/kuko/.cabal/lib/x86_64-linux-ghc-8.0.2/text-1.2.2.2-KC7dWoG09dA1F6jKj5GSqh/libHStext-1.2.2.2-KC7dWoG09dA1F6jKj5GSqh.a(cbits.o): In function `_hs_text_decode_utf8':
(.text+0x2a0): multiple definition of `_hs_text_decode_utf8'
dist/build/text-benchmarks/text-benchmarks-tmp/../cbits/cbits.o:cbits.c:(.text+0x150): first defined here
collect2: error: ld returned 1 exit status
```
The problem is, that `criterion` has `text` as a dependency.
Currently, as a workaround, I just rename the functions in `cbits.c`, then `cabal build` just works.
* Is there a better solution?
* If not, I can send a PR adding a compilation flag and do the renaming, so `cabal build` just works.
* Is this related to https://github.com/haskell/cabal/issues/1575 ?
| 1.0 | Can't build benchmarks - When trying to build benchmarks, I get a linker error, as the `cbits.c` from the `text` i have installed clash with the `cbits.c` from the `text` source code i'm currently working on and which i'm trying to benchmark.
```
Linking dist/build/text-benchmarks/text-benchmarks ...
/home/kuko/.cabal/lib/x86_64-linux-ghc-8.0.2/text-1.2.2.2-KC7dWoG09dA1F6jKj5GSqh/libHStext-1.2.2.2-KC7dWoG09dA1F6jKj5GSqh.a(cbits.o): In function `_hs_text_memcmp':
(.text+0x20): multiple definition of `_hs_text_memcmp'
dist/build/text-benchmarks/text-benchmarks-tmp/../cbits/cbits.o:cbits.c:(.text+0x0): first defined here
/home/kuko/.cabal/lib/x86_64-linux-ghc-8.0.2/text-1.2.2.2-KC7dWoG09dA1F6jKj5GSqh/libHStext-1.2.2.2-KC7dWoG09dA1F6jKj5GSqh.a(cbits.o): In function `_hs_text_decode_utf8_state':
(.text+0xe0): multiple definition of `_hs_text_decode_utf8_state'
dist/build/text-benchmarks/text-benchmarks-tmp/../cbits/cbits.o:cbits.c:(.text+0x20): first defined here
/home/kuko/.cabal/lib/x86_64-linux-ghc-8.0.2/text-1.2.2.2-KC7dWoG09dA1F6jKj5GSqh/libHStext-1.2.2.2-KC7dWoG09dA1F6jKj5GSqh.a(cbits.o): In function `_hs_text_decode_utf8':
(.text+0x2a0): multiple definition of `_hs_text_decode_utf8'
dist/build/text-benchmarks/text-benchmarks-tmp/../cbits/cbits.o:cbits.c:(.text+0x150): first defined here
collect2: error: ld returned 1 exit status
```
The problem is, that `criterion` has `text` as a dependency.
Currently, as a workaround, I just rename the functions in `cbits.c`, then `cabal build` just works.
* Is there a better solution?
* If not, I can send a PR adding a compilation flag and do the renaming, so `cabal build` just works.
* Is this related to https://github.com/haskell/cabal/issues/1575 ?
| non_priority | can t build benchmarks when trying to build benchmarks i get a linker error as the cbits c from the text i have installed clash with the cbits c from the text source code i m currently working on and which i m trying to benchmark linking dist build text benchmarks text benchmarks home kuko cabal lib linux ghc text libhstext a cbits o in function hs text memcmp text multiple definition of hs text memcmp dist build text benchmarks text benchmarks tmp cbits cbits o cbits c text first defined here home kuko cabal lib linux ghc text libhstext a cbits o in function hs text decode state text multiple definition of hs text decode state dist build text benchmarks text benchmarks tmp cbits cbits o cbits c text first defined here home kuko cabal lib linux ghc text libhstext a cbits o in function hs text decode text multiple definition of hs text decode dist build text benchmarks text benchmarks tmp cbits cbits o cbits c text first defined here error ld returned exit status the problem is that criterion has text as a dependency currently as a workaround i just rename the functions in cbits c then cabal build just works is there a better solution if not i can send a pr adding a compilation flag and do the renaming so cabal build just works is this related to | 0 |
39,634 | 5,110,572,589 | IssuesEvent | 2017-01-06 00:55:21 | httpwg/http-extensions | https://api.github.com/repos/httpwg/http-extensions | closed | Record size (rs) should be of ciphertext, not padded-plaintext | design encryption | It would be better to define the 'rs' (record size) parameter as the size of each ciphertext record (including the 16 byte tag for AEAD_AES_128_GCM).
That way a receiver can split the body into records without needing to add the algorithm-specific tag length. Then pass the bytes to a crypto library that does know details such as the tag length for a given alg.
This spec doesn't absolutely need alg agility as other algs would define their own content-encoding label. But it would be cleaner (& safer) if future algs could follow exactly the same pattern and same body format by simply defining a new content-encoding label. The format is very close, with the need to add 16 to 'rs' being the only wart. | 1.0 | Record size (rs) should be of ciphertext, not padded-plaintext - It would be better to define the 'rs' (record size) parameter as the size of each ciphertext record (including the 16 byte tag for AEAD_AES_128_GCM).
That way a receiver can split the body into records without needing to add the algorithm-specific tag length. Then pass the bytes to a crypto library that does know details such as the tag length for a given alg.
This spec doesn't absolutely need alg agility as other algs would define their own content-encoding label. But it would be cleaner (& safer) if future algs could follow exactly the same pattern and same body format by simply defining a new content-encoding label. The format is very close, with the need to add 16 to 'rs' being the only wart. | non_priority | record size rs should be of ciphertext not padded plaintext it would be better to define the rs record size parameter as the size of each ciphertext record including the byte tag for aead aes gcm that way a receiver can split the body into records without needing to add the algorithm specific tag length then pass the bytes to a crypto library that does know details such as the tag length for a given alg this spec doesn t absolutely need alg agility as other algs would define their own content encoding label but it would be cleaner safer if future algs could follow exactly the same pattern and same body format by simply defining a new content encoding label the format is very close with the need to add to rs being the only wart | 0 |
15,108 | 3,925,209,779 | IssuesEvent | 2016-04-22 18:04:56 | sys-bio/roadrunner | https://api.github.com/repos/sys-bio/roadrunner | opened | What is the difference between oneStep and Integrate? | Documentation Error question | I noticed in the docs we have oneStep and integrate, what's the difference?
| 1.0 | What is the difference between oneStep and Integrate? - I noticed in the docs we have oneStep and integrate, what's the difference?
| non_priority | what is the difference between onestep and integrate i noticed in the docs we have onestep and integrate what s the difference | 0 |
85,515 | 16,672,895,656 | IssuesEvent | 2021-06-07 13:07:52 | Regalis11/Barotrauma | https://api.github.com/repos/Regalis11/Barotrauma | opened | Gene splicing: "installing" genetic material on characters | Code Feature request | https://docs.google.com/document/d/1EvjxcXhOGrLlOvKVUfWNFRhRAB4ZU1Yxsyip3SzHs9o
> After the material has been researched, refined, and/or combined to your liking, it can be spliced into a human character. For this, the player needs a splicer that can be fabricated or bought. Genetic material is inserted into the splicer and it is then dropped onto a slot in the medical UI. The material can be removed simply by clicking on it, but it will be destroyed in the process.
Could maybe be implemented as Wearables that go into a special "gene slot" that's only visible in the health interface? | 1.0 | Gene splicing: "installing" genetic material on characters - https://docs.google.com/document/d/1EvjxcXhOGrLlOvKVUfWNFRhRAB4ZU1Yxsyip3SzHs9o
> After the material has been researched, refined, and/or combined to your liking, it can be spliced into a human character. For this, the player needs a splicer that can be fabricated or bought. Genetic material is inserted into the splicer and it is then dropped onto a slot in the medical UI. The material can be removed simply by clicking on it, but it will be destroyed in the process.
Could maybe be implemented as Wearables that go into a special "gene slot" that's only visible in the health interface? | non_priority | gene splicing installing genetic material on characters after the material has been researched refined and or combined to your liking it can be spliced into a human character for this the player needs a splicer that can be fabricated or bought genetic material is inserted into the splicer and it is then dropped onto a slot in the medical ui the material can be removed simply by clicking on it but it will be destroyed in the process could maybe be implemented as wearables that go into a special gene slot that s only visible in the health interface | 0 |
413,617 | 27,961,676,758 | IssuesEvent | 2023-03-24 16:06:10 | 0x192/universal-android-debloater | https://api.github.com/repos/0x192/universal-android-debloater | opened | com.android.statementservice update | package::documentation | **Packages documentation to update:**
```
com.android.statementservice
...
```
## Documentation chage
**Current description**
> Intent Filter Verification Service
> Intent: https://developer.android.com/reference/android/content/Intent
> Intent Filters: https://developer.android.com/guide/components/intents-filters
> https://android.stackexchange.com/questions/191163/what-does-the-intent-filter-verification-service-app-from-google-do
**Proposed description**
> Verifies that packages that want to handle URIs are certified by those websites.
> A Statement protocol allows websites to certify that some assets represent them. See: https://github.com/google/digitalassetlinks/blob/master/well-known/details.md
> Android package can to subscribe to handling chosen URIs. This package will then be called to query the website and verify that it allows this.
> https://android.googlesource.com/platform/frameworks/base/+/6a34bb2 | 1.0 | com.android.statementservice update - **Packages documentation to update:**
```
com.android.statementservice
...
```
## Documentation chage
**Current description**
> Intent Filter Verification Service
> Intent: https://developer.android.com/reference/android/content/Intent
> Intent Filters: https://developer.android.com/guide/components/intents-filters
> https://android.stackexchange.com/questions/191163/what-does-the-intent-filter-verification-service-app-from-google-do
**Proposed description**
> Verifies that packages that want to handle URIs are certified by those websites.
> A Statement protocol allows websites to certify that some assets represent them. See: https://github.com/google/digitalassetlinks/blob/master/well-known/details.md
> Android package can to subscribe to handling chosen URIs. This package will then be called to query the website and verify that it allows this.
> https://android.googlesource.com/platform/frameworks/base/+/6a34bb2 | non_priority | com android statementservice update packages documentation to update com android statementservice documentation chage current description intent filter verification service intent intent filters proposed description verifies that packages that want to handle uris are certified by those websites a statement protocol allows websites to certify that some assets represent them see android package can to subscribe to handling chosen uris this package will then be called to query the website and verify that it allows this | 0 |
52,333 | 13,747,798,820 | IssuesEvent | 2020-10-06 08:10:10 | idmarinas/lotgd-game | https://api.github.com/repos/idmarinas/lotgd-game | closed | CVE-2019-6286 (Medium) detected in opennms-opennms-source-22.0.1-1, node-sass-4.14.1.tgz - autoclosed | bug security vulnerability | ## CVE-2019-6286 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.14.1.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/lotgd-game/package.json</p>
<p>Path to vulnerable library: /lotgd-game/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.14.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/idmarinas/lotgd-game/commit/a68ef33093518f30b58ce6afc7b54944a697f707">a68ef33093518f30b58ce6afc7b54944a697f707</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass 3.5.5, a heap-based buffer over-read exists in Sass::Prelexer::skip_over_scopes in prelexer.hpp when called from Sass::Parser::parse_import(), a similar issue to CVE-2018-11693.
<p>Publish Date: 2019-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-6286>CVE-2019-6286</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-6286">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-6286</a></p>
<p>Release Date: 2019-08-06</p>
<p>Fix Resolution: LibSass - 3.6.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-6286 (Medium) detected in opennms-opennms-source-22.0.1-1, node-sass-4.14.1.tgz - autoclosed - ## CVE-2019-6286 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.14.1.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/lotgd-game/package.json</p>
<p>Path to vulnerable library: /lotgd-game/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.14.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/idmarinas/lotgd-game/commit/a68ef33093518f30b58ce6afc7b54944a697f707">a68ef33093518f30b58ce6afc7b54944a697f707</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass 3.5.5, a heap-based buffer over-read exists in Sass::Prelexer::skip_over_scopes in prelexer.hpp when called from Sass::Parser::parse_import(), a similar issue to CVE-2018-11693.
<p>Publish Date: 2019-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-6286>CVE-2019-6286</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-6286">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-6286</a></p>
<p>Release Date: 2019-08-06</p>
<p>Fix Resolution: LibSass - 3.6.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in opennms opennms source node sass tgz autoclosed cve medium severity vulnerability vulnerable libraries node sass tgz node sass tgz wrapper around libsass library home page a href path to dependency file tmp ws scm lotgd game package json path to vulnerable library lotgd game node modules node sass package json dependency hierarchy x node sass tgz vulnerable library found in head commit a href vulnerability details in libsass a heap based buffer over read exists in sass prelexer skip over scopes in prelexer hpp when called from sass parser parse import a similar issue to cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution libsass step up your open source security game with whitesource | 0 |
46,124 | 13,055,855,614 | IssuesEvent | 2020-07-30 02:56:16 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | opened | I3Tray finish gets called due to exceptions in constructors/Configure methods (Trac #615) | IceTray Incomplete Migration Migrated from Trac defect | Migrated from https://code.icecube.wisc.edu/ticket/615
```json
{
"status": "closed",
"changetime": "2012-10-31T20:57:48",
"description": "An exception in service or module constructors causes I3Finish to be called without there being a driving module yet, which seems to confuse I3Finish and makes it throw its own exception. The resulting second exception could be confusing to users..\n\n\n\nHere is an example of how this looks like on the standard output:\n\nlilliput/private/minimizer/I3GSLMultiMin.cxx:105: ERROR: The \"vector_bfgs2\" minimizer is not available in your version of GSL. Update to version 1.14 or newer.\n/lilliput/private/minimizer/I3GSLMultiMin.cxx:189: FATAL: Unknown minimizer algorithm \"vector_bfgs2\"!\nTraceback (most recent call last):\n File \"./aartfit.py\", line 553, in <module>\n tray.Execute()\n File \"/Users/claudio/Documents/Uni/IceTray/test/build.searecsim.release/lib/I3Tray.py\", line 118, in Execute\n args[0].the_tray.Execute()\nRuntimeError: Unknown minimizer algorithm \"vector_bfgs2\"!\nI3Tray finishing...\n/icetray/private/icetray/I3Tray.cxx:457: FATAL: Attempt to call finish, but there is no driving module. Did you forget to call Execute()?\nterminate called after throwing an instance of 'std::runtime_error'\n what(): Attempt to call finish, but there is no driving module. Did you forget to call Execute()?\nAbort trap\n",
"reporter": "icecube",
"cc": "claudio.kopper@physik.uni-erlangen.de",
"resolution": "fixed",
"_ts": "1351717068000000",
"component": "IceTray",
"summary": "I3Tray finish gets called due to exceptions in constructors/Configure methods",
"priority": "normal",
"keywords": "",
"time": "2010-07-30T10:11:17",
"milestone": "",
"owner": "troy",
"type": "defect"
}
```
| 1.0 | I3Tray finish gets called due to exceptions in constructors/Configure methods (Trac #615) - Migrated from https://code.icecube.wisc.edu/ticket/615
```json
{
"status": "closed",
"changetime": "2012-10-31T20:57:48",
"description": "An exception in service or module constructors causes I3Finish to be called without there being a driving module yet, which seems to confuse I3Finish and makes it throw its own exception. The resulting second exception could be confusing to users..\n\n\n\nHere is an example of how this looks like on the standard output:\n\nlilliput/private/minimizer/I3GSLMultiMin.cxx:105: ERROR: The \"vector_bfgs2\" minimizer is not available in your version of GSL. Update to version 1.14 or newer.\n/lilliput/private/minimizer/I3GSLMultiMin.cxx:189: FATAL: Unknown minimizer algorithm \"vector_bfgs2\"!\nTraceback (most recent call last):\n File \"./aartfit.py\", line 553, in <module>\n tray.Execute()\n File \"/Users/claudio/Documents/Uni/IceTray/test/build.searecsim.release/lib/I3Tray.py\", line 118, in Execute\n args[0].the_tray.Execute()\nRuntimeError: Unknown minimizer algorithm \"vector_bfgs2\"!\nI3Tray finishing...\n/icetray/private/icetray/I3Tray.cxx:457: FATAL: Attempt to call finish, but there is no driving module. Did you forget to call Execute()?\nterminate called after throwing an instance of 'std::runtime_error'\n what(): Attempt to call finish, but there is no driving module. Did you forget to call Execute()?\nAbort trap\n",
"reporter": "icecube",
"cc": "claudio.kopper@physik.uni-erlangen.de",
"resolution": "fixed",
"_ts": "1351717068000000",
"component": "IceTray",
"summary": "I3Tray finish gets called due to exceptions in constructors/Configure methods",
"priority": "normal",
"keywords": "",
"time": "2010-07-30T10:11:17",
"milestone": "",
"owner": "troy",
"type": "defect"
}
```
| non_priority | finish gets called due to exceptions in constructors configure methods trac migrated from json status closed changetime description an exception in service or module constructors causes to be called without there being a driving module yet which seems to confuse and makes it throw its own exception the resulting second exception could be confusing to users n n n nhere is an example of how this looks like on the standard output n nlilliput private minimizer cxx error the vector minimizer is not available in your version of gsl update to version or newer n lilliput private minimizer cxx fatal unknown minimizer algorithm vector ntraceback most recent call last n file aartfit py line in n tray execute n file users claudio documents uni icetray test build searecsim release lib py line in execute n args the tray execute nruntimeerror unknown minimizer algorithm vector finishing n icetray private icetray cxx fatal attempt to call finish but there is no driving module did you forget to call execute nterminate called after throwing an instance of std runtime error n what attempt to call finish but there is no driving module did you forget to call execute nabort trap n reporter icecube cc claudio kopper physik uni erlangen de resolution fixed ts component icetray summary finish gets called due to exceptions in constructors configure methods priority normal keywords time milestone owner troy type defect | 0 |
260,888 | 19,687,793,365 | IssuesEvent | 2022-01-12 01:08:58 | imAsparky/django-cookiecutter | https://api.github.com/repos/imAsparky/django-cookiecutter | closed | [DOCS]: Create How-to use postgress in place of the default SQLite in test the environment. | documentation | **Describe alternatives you've considered**
Would you please share your clear and concise description of any alternative/similar documentation you've considered.
**Additional context**
Would you please share any other context or screenshots about the documentation request here.
By default, SQLite is used in the test environment to make it easier for
1. Quick local development without the need to set up Postgress and
2. new Django users.
It should be easy for users to get this done without digging amongst code.
| 1.0 | [DOCS]: Create How-to use postgress in place of the default SQLite in test the environment. - **Describe alternatives you've considered**
Would you please share your clear and concise description of any alternative/similar documentation you've considered.
**Additional context**
Would you please share any other context or screenshots about the documentation request here.
By default, SQLite is used in the test environment to make it easier for
1. Quick local development without the need to set up Postgress and
2. new Django users.
It should be easy for users to get this done without digging amongst code.
| non_priority | create how to use postgress in place of the default sqlite in test the environment describe alternatives you ve considered would you please share your clear and concise description of any alternative similar documentation you ve considered additional context would you please share any other context or screenshots about the documentation request here by default sqlite is used in the test environment to make it easier for quick local development without the need to set up postgress and new django users it should be easy for users to get this done without digging amongst code | 0 |
27,047 | 6,813,268,053 | IssuesEvent | 2017-11-06 08:34:05 | BTDF/DeploymentFramework | https://api.github.com/repos/BTDF/DeploymentFramework | closed | Add additional extensibility points by creating more overridable targets | CodePlexMigrationInitiated enhancement General Impact: Low Release 5.0 | Add additional extensibility points by creating more overridable targets -- along the lines of today's CustomPostDeployTarget. Add CustomPreExportSettings, CustomPostExportSettings, CustomPreInitialize, CustomPostInitialize.
#### This work item was migrated from CodePlex
CodePlex work item ID: '7854'
Assigned to: 'tfabraham'
Vote count: '2'
| 1.0 | Add additional extensibility points by creating more overridable targets - Add additional extensibility points by creating more overridable targets -- along the lines of today's CustomPostDeployTarget. Add CustomPreExportSettings, CustomPostExportSettings, CustomPreInitialize, CustomPostInitialize.
#### This work item was migrated from CodePlex
CodePlex work item ID: '7854'
Assigned to: 'tfabraham'
Vote count: '2'
| non_priority | add additional extensibility points by creating more overridable targets add additional extensibility points by creating more overridable targets along the lines of today s custompostdeploytarget add custompreexportsettings custompostexportsettings custompreinitialize custompostinitialize this work item was migrated from codeplex codeplex work item id assigned to tfabraham vote count | 0 |
15,404 | 9,547,710,556 | IssuesEvent | 2019-05-02 00:48:34 | notepad-plus-plus/notepad-plus-plus | https://api.github.com/repos/notepad-plus-plus/notepad-plus-plus | closed | Auto-update is insecure (no https) | security | ### Description of the Issue
Notepad++ fetches data about a new release from
> https://notepad-plus-plus.org/update/getDownloadUrl.php
(as specified [here](https://github.com/notepad-plus-plus/notepad-plus-plus/blob/master/PowerEditor/bin/updater/gup.xml)) and that file provides the URL
> http://notepad-plus-plus.org/repository/7.x/7.5.4/npp.7.5.4.Installer.exe
to download the installer. While we get a secure* info about the current version, the installer itself is downloaded over an insecure channel. This allows remote attackers on the network layer (like any shared or public WLAN) to inject any malware they like.
The problem becomes worse since the Notepad++ installer is not digitally signed and the only source of trust is the originating website. Where I cannot see the originating website, I have to trust that the application performs the relevant checks for me – and it doesn't.
*) I hope that SSL certificate checking is done properly for it to have any use.
| True | Auto-update is insecure (no https) - ### Description of the Issue
Notepad++ fetches data about a new release from
> https://notepad-plus-plus.org/update/getDownloadUrl.php
(as specified [here](https://github.com/notepad-plus-plus/notepad-plus-plus/blob/master/PowerEditor/bin/updater/gup.xml)) and that file provides the URL
> http://notepad-plus-plus.org/repository/7.x/7.5.4/npp.7.5.4.Installer.exe
to download the installer. While we get a secure* info about the current version, the installer itself is downloaded over an insecure channel. This allows remote attackers on the network layer (like any shared or public WLAN) to inject any malware they like.
The problem becomes worse since the Notepad++ installer is not digitally signed and the only source of trust is the originating website. Where I cannot see the originating website, I have to trust that the application performs the relevant checks for me – and it doesn't.
*) I hope that SSL certificate checking is done properly for it to have any use.
| non_priority | auto update is insecure no https description of the issue notepad fetches data about a new release from as specified and that file provides the url to download the installer while we get a secure info about the current version the installer itself is downloaded over an insecure channel this allows remote attackers on the network layer like any shared or public wlan to inject any malware they like the problem becomes worse since the notepad installer is not digitally signed and the only source of trust is the originating website where i cannot see the originating website i have to trust that the application performs the relevant checks for me – and it doesn t i hope that ssl certificate checking is done properly for it to have any use | 0 |
5,982 | 4,107,609,531 | IssuesEvent | 2016-06-06 13:38:41 | cul-it/mann-wagon | https://api.github.com/repos/cul-it/mann-wagon | closed | Usability Task for Study Room Availability | Epic usability | 1. Are there any individual study rooms available at Mann right now?
1. If not, when is the next one available?
> How would you claim this room? | True | Usability Task for Study Room Availability - 1. Are there any individual study rooms available at Mann right now?
1. If not, when is the next one available?
> How would you claim this room? | non_priority | usability task for study room availability are there any individual study rooms available at mann right now if not when is the next one available how would you claim this room | 0 |
152,726 | 13,465,508,651 | IssuesEvent | 2020-09-09 20:59:58 | adobe/spectrum-css | https://api.github.com/repos/adobe/spectrum-css | closed | Release date hardcoded on documentation site | documentation sync to jira | ## Description
<!-- Describe what's missing, unclear, or incorrect -->
Release dates are currently hardcoded.
## Link to documentation
<!-- Paste the link to the document where the issue exists -->
https://opensource.adobe.com/spectrum-css/components/button-cta/
## Additional context
<!-- Provide any additional information that might help us understand the issue -->
In order to get the site out the door, the release dates were hardcoded. They need to be updated to use npm or git tags to determine dates.
synced to jira: https://jira.corp.adobe.com/browse/SDS-7334 | 1.0 | Release date hardcoded on documentation site - ## Description
<!-- Describe what's missing, unclear, or incorrect -->
Release dates are currently hardcoded.
## Link to documentation
<!-- Paste the link to the document where the issue exists -->
https://opensource.adobe.com/spectrum-css/components/button-cta/
## Additional context
<!-- Provide any additional information that might help us understand the issue -->
In order to get the site out the door, the release dates were hardcoded. They need to be updated to use npm or git tags to determine dates.
synced to jira: https://jira.corp.adobe.com/browse/SDS-7334 | non_priority | release date hardcoded on documentation site description release dates are currently hardcoded link to documentation additional context in order to get the site out the door the release dates were hardcoded they need to be updated to use npm or git tags to determine dates synced to jira | 0 |
34,313 | 16,517,464,333 | IssuesEvent | 2021-05-26 11:16:18 | fgpv-vpgf/fgpv-vpgf | https://api.github.com/repos/fgpv-vpgf/fgpv-vpgf | closed | FGP not responding when uploaded file size reached 7MB | needs: more info problem: performance type: corrective | Tested on http://fgpv.cloudapp.net/demo/v0.18.0-4/index-fgp-en.html?keys=JOSM,EcoAction,CESI_Other,NPRI_CO,Railways,mb_colour,Airports,Barley
Uploaded a CSV file 521.csv (7231KB) will cause the map not responding. Need to know the system limitation?

| True | FGP not responding when uploaded file size reached 7MB - Tested on http://fgpv.cloudapp.net/demo/v0.18.0-4/index-fgp-en.html?keys=JOSM,EcoAction,CESI_Other,NPRI_CO,Railways,mb_colour,Airports,Barley
Uploaded a CSV file 521.csv (7231KB) will cause the map not responding. Need to know the system limitation?

| non_priority | fgp not responding when uploaded file size reached tested on uploaded a csv file csv will cause the map not responding need to know the system limitation | 0 |
67,535 | 27,878,690,073 | IssuesEvent | 2023-03-21 17:42:16 | hashicorp/terraform-provider-aws | https://api.github.com/repos/hashicorp/terraform-provider-aws | closed | data aws_s3_bucket_object doesn't read s3 object (inconsistent behaviour) | enhancement service/s3 stale | <!---
Please note the following potential times when an issue might be in Terraform core:
* [Configuration Language](https://www.terraform.io/docs/configuration/index.html) or resource ordering issues
* [State](https://www.terraform.io/docs/state/index.html) and [State Backend](https://www.terraform.io/docs/backends/index.html) issues
* [Provisioner](https://www.terraform.io/docs/provisioners/index.html) issues
* [Registry](https://registry.terraform.io/) issues
* Spans resources across multiple providers
If you are running into one of these scenarios, we recommend opening an issue in the [Terraform core repository](https://github.com/hashicorp/terraform/) instead.
--->
<!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or other comments that do not add relevant new information or questions, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Terraform CLI and Terraform AWS Provider Version
<!--- Please run `terraform -v` to show the Terraform core version and provider version(s). If you are not running the latest version of Terraform or the provider, please upgrade because your issue may have already been fixed. [Terraform documentation on provider versioning](https://www.terraform.io/docs/configuration/providers.html#provider-versions). --->
```bash
❯ terraform version
Terraform v0.14.7
+ provider registry.terraform.io/hashicorp/aws v3.29.1
```
### Affected Resource(s)
<!--- Please list the affected resources and data sources. --->
* [data "aws_s3_bucket_object"](https://registry.terraform.io/providers/hashicorp/aws/latest/docs/data-sources/s3_bucket_object)
### Terraform Configuration Files
<!--- Information about code formatting: https://help.github.com/articles/basic-writing-and-formatting-syntax/#quoting-code --->
Please include all Terraform configurations required to reproduce the bug. Bug reports without a functional reproduction may be closed without investigation.
```hcl
data "aws_s3_bucket_object" "json_values" {
bucket = var.s3_bucket
# This does not work "ContentType": "binary/octet-stream" but work with "ContentType": "application/json"
key = "folder/subfolder/outputs.json"
# This works for both "ContentType": "binary/octet-stream" and "ContentType": "application/json"
key = "outputs.json"
}
```
### Expected Behavior
The behaviour should be consistent with root level keys or nested keys in the s3 bucket
### Actual Behavior
`data.aws_s3_bucket_object.json_values.body` is empty when "ContentType": "binary/octet-stream" in nested keys.
### Steps to Reproduce
<!--- Please list the steps required to reproduce the issue. --->
1. `terraform init`
2. `terraform apply`
### References
<!---
Information about referencing Github Issues: https://help.github.com/articles/basic-writing-and-formatting-syntax/#referencing-issues-and-pull-requests
Are there any other GitHub issues (open or closed) or pull requests that should be linked here? Vendor documentation? For example:
--->
* #5248
| 1.0 | data aws_s3_bucket_object doesn't read s3 object (inconsistent behaviour) - <!---
Please note the following potential times when an issue might be in Terraform core:
* [Configuration Language](https://www.terraform.io/docs/configuration/index.html) or resource ordering issues
* [State](https://www.terraform.io/docs/state/index.html) and [State Backend](https://www.terraform.io/docs/backends/index.html) issues
* [Provisioner](https://www.terraform.io/docs/provisioners/index.html) issues
* [Registry](https://registry.terraform.io/) issues
* Spans resources across multiple providers
If you are running into one of these scenarios, we recommend opening an issue in the [Terraform core repository](https://github.com/hashicorp/terraform/) instead.
--->
<!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or other comments that do not add relevant new information or questions, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Terraform CLI and Terraform AWS Provider Version
<!--- Please run `terraform -v` to show the Terraform core version and provider version(s). If you are not running the latest version of Terraform or the provider, please upgrade because your issue may have already been fixed. [Terraform documentation on provider versioning](https://www.terraform.io/docs/configuration/providers.html#provider-versions). --->
```bash
❯ terraform version
Terraform v0.14.7
+ provider registry.terraform.io/hashicorp/aws v3.29.1
```
### Affected Resource(s)
<!--- Please list the affected resources and data sources. --->
* [data "aws_s3_bucket_object"](https://registry.terraform.io/providers/hashicorp/aws/latest/docs/data-sources/s3_bucket_object)
### Terraform Configuration Files
<!--- Information about code formatting: https://help.github.com/articles/basic-writing-and-formatting-syntax/#quoting-code --->
Please include all Terraform configurations required to reproduce the bug. Bug reports without a functional reproduction may be closed without investigation.
```hcl
data "aws_s3_bucket_object" "json_values" {
bucket = var.s3_bucket
# This does not work "ContentType": "binary/octet-stream" but work with "ContentType": "application/json"
key = "folder/subfolder/outputs.json"
# This works for both "ContentType": "binary/octet-stream" and "ContentType": "application/json"
key = "outputs.json"
}
```
### Expected Behavior
The behaviour should be consistent with root level keys or nested keys in the s3 bucket
### Actual Behavior
`data.aws_s3_bucket_object.json_values.body` is empty when "ContentType": "binary/octet-stream" in nested keys.
### Steps to Reproduce
<!--- Please list the steps required to reproduce the issue. --->
1. `terraform init`
2. `terraform apply`
### References
<!---
Information about referencing Github Issues: https://help.github.com/articles/basic-writing-and-formatting-syntax/#referencing-issues-and-pull-requests
Are there any other GitHub issues (open or closed) or pull requests that should be linked here? Vendor documentation? For example:
--->
* #5248
| non_priority | data aws bucket object doesn t read object inconsistent behaviour please note the following potential times when an issue might be in terraform core or resource ordering issues and issues issues issues spans resources across multiple providers if you are running into one of these scenarios we recommend opening an issue in the instead community note please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request please do not leave or other comments that do not add relevant new information or questions they generate extra noise for issue followers and do not help prioritize the request if you are interested in working on this issue or have submitted a pull request please leave a comment terraform cli and terraform aws provider version bash ❯ terraform version terraform provider registry terraform io hashicorp aws affected resource s terraform configuration files please include all terraform configurations required to reproduce the bug bug reports without a functional reproduction may be closed without investigation hcl data aws bucket object json values bucket var bucket this does not work contenttype binary octet stream but work with contenttype application json key folder subfolder outputs json this works for both contenttype binary octet stream and contenttype application json key outputs json expected behavior the behaviour should be consistent with root level keys or nested keys in the bucket actual behavior data aws bucket object json values body is empty when contenttype binary octet stream in nested keys steps to reproduce terraform init terraform apply references information about referencing github issues are there any other github issues open or closed or pull requests that should be linked here vendor documentation for example | 0 |
21,396 | 17,019,054,189 | IssuesEvent | 2021-07-02 15:57:01 | RecordReplay/gecko-dev | https://api.github.com/repos/RecordReplay/gecko-dev | closed | Improve recording error page | usability | With recent changes to gecko-dev and the backend, if we have a problem where the recording becomes unusable because of a connection problem with the server or unsupported activity in the recording process (like a stack overflow), we show an error page instead of the recording process crashing/hanging. This error page is pretty rough though, see the screen below (the associated code is in aboutReplay.js and associated files).
<img width="798" alt="Screen Shot 2020-10-27 at 9 08 48 AM" src="https://user-images.githubusercontent.com/1062578/97322798-c311f780-1835-11eb-83f5-936edb674083.png">
| True | Improve recording error page - With recent changes to gecko-dev and the backend, if we have a problem where the recording becomes unusable because of a connection problem with the server or unsupported activity in the recording process (like a stack overflow), we show an error page instead of the recording process crashing/hanging. This error page is pretty rough though, see the screen below (the associated code is in aboutReplay.js and associated files).
<img width="798" alt="Screen Shot 2020-10-27 at 9 08 48 AM" src="https://user-images.githubusercontent.com/1062578/97322798-c311f780-1835-11eb-83f5-936edb674083.png">
| non_priority | improve recording error page with recent changes to gecko dev and the backend if we have a problem where the recording becomes unusable because of a connection problem with the server or unsupported activity in the recording process like a stack overflow we show an error page instead of the recording process crashing hanging this error page is pretty rough though see the screen below the associated code is in aboutreplay js and associated files img width alt screen shot at am src | 0 |
56,741 | 6,528,358,014 | IssuesEvent | 2017-08-30 07:09:53 | elastic/logstash | https://api.github.com/repos/elastic/logstash | closed | Test failure: require order in environment.rb incorrect when xpack is running specs | bug test failure v6.0.0 v6.1.0 | ```
NameError:
uninitialized constant LogStash::Environment
Did you mean? LogStash::EnvironmentError
# /var/lib/jenkins/workspace/elastic+x-pack-logstash+6.0+periodic/logstash/logstash-core/lib/logstash/util.rb:150:in `<module:Util>'
# /var/lib/jenkins/workspace/elastic+x-pack-logstash+6.0+periodic/logstash/logstash-core/lib/logstash/util.rb:5:in `<main>'
# /var/lib/jenkins/workspace/elastic+x-pack-logstash+6.0+periodic/logstash/logstash-core/lib/logstash/util/password.rb:1:in `<main>'
# /var/lib/jenkins/workspace/elastic+x-pack-logstash+6.0+periodic/logstash/logstash-core/lib/logstash/util/password.rb:3:in `<main>'
# /var/lib/jenkins/workspace/elastic+x-pack-logstash+6.0+periodic/logstash/logstash-core/lib/logstash/util/cloud_setting_auth.rb:1:in `<main>'
# /var/lib/jenkins/workspace/elastic+x-pack-logstash+6.0+periodic/logstash/logstash-core/lib/logstash/util/cloud_setting_auth.rb:3:in `<main>'
# /var/lib/jenkins/workspace/elastic+x-pack-logstash+6.0+periodic/logstash/logstash-core/lib/logstash/environment.rb:1:in `<main>'
# /var/lib/jenkins/workspace/elastic+x-pack-logstash+6.0+periodic/logstash/logstash-core/lib/logstash/environment.rb:7:in `<main>'
...
An error occurred while loading /var/lib/jenkins/workspace/elastic+x-pack-logstash+6.0+periodic/logstash-extra/x-pack-logstash/spec/config_management/elasticsearch_source_spec.rb
``` | 1.0 | Test failure: require order in environment.rb incorrect when xpack is running specs - ```
NameError:
uninitialized constant LogStash::Environment
Did you mean? LogStash::EnvironmentError
# /var/lib/jenkins/workspace/elastic+x-pack-logstash+6.0+periodic/logstash/logstash-core/lib/logstash/util.rb:150:in `<module:Util>'
# /var/lib/jenkins/workspace/elastic+x-pack-logstash+6.0+periodic/logstash/logstash-core/lib/logstash/util.rb:5:in `<main>'
# /var/lib/jenkins/workspace/elastic+x-pack-logstash+6.0+periodic/logstash/logstash-core/lib/logstash/util/password.rb:1:in `<main>'
# /var/lib/jenkins/workspace/elastic+x-pack-logstash+6.0+periodic/logstash/logstash-core/lib/logstash/util/password.rb:3:in `<main>'
# /var/lib/jenkins/workspace/elastic+x-pack-logstash+6.0+periodic/logstash/logstash-core/lib/logstash/util/cloud_setting_auth.rb:1:in `<main>'
# /var/lib/jenkins/workspace/elastic+x-pack-logstash+6.0+periodic/logstash/logstash-core/lib/logstash/util/cloud_setting_auth.rb:3:in `<main>'
# /var/lib/jenkins/workspace/elastic+x-pack-logstash+6.0+periodic/logstash/logstash-core/lib/logstash/environment.rb:1:in `<main>'
# /var/lib/jenkins/workspace/elastic+x-pack-logstash+6.0+periodic/logstash/logstash-core/lib/logstash/environment.rb:7:in `<main>'
...
An error occurred while loading /var/lib/jenkins/workspace/elastic+x-pack-logstash+6.0+periodic/logstash-extra/x-pack-logstash/spec/config_management/elasticsearch_source_spec.rb
``` | non_priority | test failure require order in environment rb incorrect when xpack is running specs nameerror uninitialized constant logstash environment did you mean logstash environmenterror var lib jenkins workspace elastic x pack logstash periodic logstash logstash core lib logstash util rb in var lib jenkins workspace elastic x pack logstash periodic logstash logstash core lib logstash util rb in var lib jenkins workspace elastic x pack logstash periodic logstash logstash core lib logstash util password rb in var lib jenkins workspace elastic x pack logstash periodic logstash logstash core lib logstash util password rb in var lib jenkins workspace elastic x pack logstash periodic logstash logstash core lib logstash util cloud setting auth rb in var lib jenkins workspace elastic x pack logstash periodic logstash logstash core lib logstash util cloud setting auth rb in var lib jenkins workspace elastic x pack logstash periodic logstash logstash core lib logstash environment rb in var lib jenkins workspace elastic x pack logstash periodic logstash logstash core lib logstash environment rb in an error occurred while loading var lib jenkins workspace elastic x pack logstash periodic logstash extra x pack logstash spec config management elasticsearch source spec rb | 0 |
22,261 | 11,712,028,495 | IssuesEvent | 2020-03-09 07:15:42 | terraform-providers/terraform-provider-azurerm | https://api.github.com/repos/terraform-providers/terraform-provider-azurerm | closed | Power off VM before de-allocation | question service/virtual-machine | This is a followup to #4920 which documents much of the use case (but is now locked).
In v2 of the provider, how do we tell terraform to power-off a VM before de-allocating it? This would eliminate paying for the resource while Azure takes 10-30 minutes to de-allocate the VM.
I've looked at the parameters in https://www.terraform.io/docs/providers/azurerm/r/linux_virtual_machine.html but can't find anything. | 1.0 | Power off VM before de-allocation - This is a followup to #4920 which documents much of the use case (but is now locked).
In v2 of the provider, how do we tell terraform to power-off a VM before de-allocating it? This would eliminate paying for the resource while Azure takes 10-30 minutes to de-allocate the VM.
I've looked at the parameters in https://www.terraform.io/docs/providers/azurerm/r/linux_virtual_machine.html but can't find anything. | non_priority | power off vm before de allocation this is a followup to which documents much of the use case but is now locked in of the provider how do we tell terraform to power off a vm before de allocating it this would eliminate paying for the resource while azure takes minutes to de allocate the vm i ve looked at the parameters in but can t find anything | 0 |
60,924 | 7,430,636,228 | IssuesEvent | 2018-03-25 04:42:13 | Loopring/protocol | https://api.github.com/repos/Loopring/protocol | closed | Wallet get a percentage of mining income. | design-review enhancement | The current design of Loopring has a nice incentive mechanism for ring-miners. But it doesn't really offer any reward for wallets and website that help user to manage their orders.
We can provide such an incentive mechanism, by allowing wallet to supply an address in the order to split the fee or margin-split with miners. The percentage of LRC or margin-split should be configurable upon deployment. | 1.0 | Wallet get a percentage of mining income. - The current design of Loopring has a nice incentive mechanism for ring-miners. But it doesn't really offer any reward for wallets and website that help user to manage their orders.
We can provide such an incentive mechanism, by allowing wallet to supply an address in the order to split the fee or margin-split with miners. The percentage of LRC or margin-split should be configurable upon deployment. | non_priority | wallet get a percentage of mining income the current design of loopring has a nice incentive mechanism for ring miners but it doesn t really offer any reward for wallets and website that help user to manage their orders we can provide such an incentive mechanism by allowing wallet to supply an address in the order to split the fee or margin split with miners the percentage of lrc or margin split should be configurable upon deployment | 0 |
122,110 | 12,141,541,970 | IssuesEvent | 2020-04-23 22:50:05 | f8kgl/swr_power_meter | https://api.github.com/repos/f8kgl/swr_power_meter | closed | Comparatif des différentes solutions de calibration | documentation enhancement question | 1/Par implémentation de routines mathématiques dans le fw de test #67
Afficher le résultat de ce calcul sur le LCD
Relever les temps d'éxecution, et l'afficher sur le LCD
Implémentation du bouton poussoir, initialement prévue pour le commutateur de bande, pour basculer entre l'affichage des ADC, et l'affichage du calcul de P dans le firmware de test
Compatibilité BLU ?
2/Par implémentation d'une table
Quelle taille ?
Combien de table par rapport au choix de la bande de fréquence, choix du calibre, port FWD et REV ?
Besoin d'une EEP Ext ? quel impact sur le choix du MCU ?
=> à reporter dans la spec #23 | 1.0 | Comparatif des différentes solutions de calibration - 1/Par implémentation de routines mathématiques dans le fw de test #67
Afficher le résultat de ce calcul sur le LCD
Relever les temps d'éxecution, et l'afficher sur le LCD
Implémentation du bouton poussoir, initialement prévue pour le commutateur de bande, pour basculer entre l'affichage des ADC, et l'affichage du calcul de P dans le firmware de test
Compatibilité BLU ?
2/Par implémentation d'une table
Quelle taille ?
Combien de table par rapport au choix de la bande de fréquence, choix du calibre, port FWD et REV ?
Besoin d'une EEP Ext ? quel impact sur le choix du MCU ?
=> à reporter dans la spec #23 | non_priority | comparatif des différentes solutions de calibration par implémentation de routines mathématiques dans le fw de test afficher le résultat de ce calcul sur le lcd relever les temps d éxecution et l afficher sur le lcd implémentation du bouton poussoir initialement prévue pour le commutateur de bande pour basculer entre l affichage des adc et l affichage du calcul de p dans le firmware de test compatibilité blu par implémentation d une table quelle taille combien de table par rapport au choix de la bande de fréquence choix du calibre port fwd et rev besoin d une eep ext quel impact sur le choix du mcu à reporter dans la spec | 0 |
105,142 | 16,624,141,123 | IssuesEvent | 2021-06-03 07:26:53 | Thanraj/OpenSSL_1.0.1b | https://api.github.com/repos/Thanraj/OpenSSL_1.0.1b | opened | CVE-2016-0702 (Medium) detected in opensslOpenSSL_1_0_1b | security vulnerability | ## CVE-2016-0702 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opensslOpenSSL_1_0_1b</b></p></summary>
<p>
<p>TLS/SSL and crypto library</p>
<p>Library home page: <a href=https://github.com/openssl/openssl.git>https://github.com/openssl/openssl.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Thanraj/OpenSSL_1.0.1b/commit/bf797b6ab2ac1c03c1ac5a4724e1cbaf467d80f9">bf797b6ab2ac1c03c1ac5a4724e1cbaf467d80f9</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>OpenSSL_1.0.1b/crypto/bn/bn_exp.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>OpenSSL_1.0.1b/crypto/bn/bn_exp.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The MOD_EXP_CTIME_COPY_FROM_PREBUF function in crypto/bn/bn_exp.c in OpenSSL 1.0.1 before 1.0.1s and 1.0.2 before 1.0.2g does not properly consider cache-bank access times during modular exponentiation, which makes it easier for local users to discover RSA keys by running a crafted application on the same Intel Sandy Bridge CPU core as a victim and leveraging cache-bank conflicts, aka a "CacheBleed" attack.
<p>Publish Date: 2016-03-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-0702>CVE-2016-0702</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-0702">https://nvd.nist.gov/vuln/detail/CVE-2016-0702</a></p>
<p>Release Date: 2016-03-03</p>
<p>Fix Resolution: 1.0.1s,1.0.2g</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2016-0702 (Medium) detected in opensslOpenSSL_1_0_1b - ## CVE-2016-0702 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opensslOpenSSL_1_0_1b</b></p></summary>
<p>
<p>TLS/SSL and crypto library</p>
<p>Library home page: <a href=https://github.com/openssl/openssl.git>https://github.com/openssl/openssl.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Thanraj/OpenSSL_1.0.1b/commit/bf797b6ab2ac1c03c1ac5a4724e1cbaf467d80f9">bf797b6ab2ac1c03c1ac5a4724e1cbaf467d80f9</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>OpenSSL_1.0.1b/crypto/bn/bn_exp.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>OpenSSL_1.0.1b/crypto/bn/bn_exp.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The MOD_EXP_CTIME_COPY_FROM_PREBUF function in crypto/bn/bn_exp.c in OpenSSL 1.0.1 before 1.0.1s and 1.0.2 before 1.0.2g does not properly consider cache-bank access times during modular exponentiation, which makes it easier for local users to discover RSA keys by running a crafted application on the same Intel Sandy Bridge CPU core as a victim and leveraging cache-bank conflicts, aka a "CacheBleed" attack.
<p>Publish Date: 2016-03-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-0702>CVE-2016-0702</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-0702">https://nvd.nist.gov/vuln/detail/CVE-2016-0702</a></p>
<p>Release Date: 2016-03-03</p>
<p>Fix Resolution: 1.0.1s,1.0.2g</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in opensslopenssl cve medium severity vulnerability vulnerable library opensslopenssl tls ssl and crypto library library home page a href found in head commit a href found in base branch master vulnerable source files openssl crypto bn bn exp c openssl crypto bn bn exp c vulnerability details the mod exp ctime copy from prebuf function in crypto bn bn exp c in openssl before and before does not properly consider cache bank access times during modular exponentiation which makes it easier for local users to discover rsa keys by running a crafted application on the same intel sandy bridge cpu core as a victim and leveraging cache bank conflicts aka a cachebleed attack publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
78,657 | 9,781,838,493 | IssuesEvent | 2019-06-07 21:02:02 | Opentrons/opentrons | https://api.github.com/repos/Opentrons/opentrons | opened | PD: Indicate Deprecated Labware | feature protocol designer | As a Protocol Designer, I would like to know what labware is deprecated, so that I can consider replacing it in my protocols.
## Acceptance Criteria
- [ ] Deprecated labware should include 'Deprecated - ' in the labware display name
- [ ] Deprecated labware should still be displayed in the PD labware browser
## Deprecated Labware:
96-PCR-flat
PCR-strip-tall
opentrons-aluminum-block-2ml-eppendorf
trash-box
| 1.0 | PD: Indicate Deprecated Labware - As a Protocol Designer, I would like to know what labware is deprecated, so that I can consider replacing it in my protocols.
## Acceptance Criteria
- [ ] Deprecated labware should include 'Deprecated - ' in the labware display name
- [ ] Deprecated labware should still be displayed in the PD labware browser
## Deprecated Labware:
96-PCR-flat
PCR-strip-tall
opentrons-aluminum-block-2ml-eppendorf
trash-box
| non_priority | pd indicate deprecated labware as a protocol designer i would like to know what labware is deprecated so that i can consider replacing it in my protocols acceptance criteria deprecated labware should include deprecated in the labware display name deprecated labware should still be displayed in the pd labware browser deprecated labware pcr flat pcr strip tall opentrons aluminum block eppendorf trash box | 0 |
47,090 | 11,954,391,349 | IssuesEvent | 2020-04-03 23:29:19 | PyAr/wiki | https://api.github.com/repos/PyAr/wiki | closed | Buscar reemplazante para `[[twitter(` | build-errors | Algunas paginas tienen un `[[twitter(`
Deberiamos buscar un reemplazante en rST | 1.0 | Buscar reemplazante para `[[twitter(` - Algunas paginas tienen un `[[twitter(`
Deberiamos buscar un reemplazante en rST | non_priority | buscar reemplazante para twitter algunas paginas tienen un twitter deberiamos buscar un reemplazante en rst | 0 |
169,870 | 20,841,960,628 | IssuesEvent | 2022-03-21 01:57:41 | camcrosbie/Angular-GettingStarted | https://api.github.com/repos/camcrosbie/Angular-GettingStarted | opened | CVE-2022-24772 (High) detected in node-forge-0.10.0.tgz | security vulnerability | ## CVE-2022-24772 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-forge-0.10.0.tgz</b></p></summary>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz</a></p>
<p>Path to dependency file: /APM-Start/package.json</p>
<p>Path to vulnerable library: /APM-Start/node_modules/node-forge/package.json,/APM-Final/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.1102.3.tgz (Root Library)
- webpack-dev-server-3.11.2.tgz
- selfsigned-1.10.8.tgz
- :x: **node-forge-0.10.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Forge (also called `node-forge`) is a native implementation of Transport Layer Security in JavaScript. Prior to version 1.3.0, RSA PKCS#1 v1.5 signature verification code does not check for tailing garbage bytes after decoding a `DigestInfo` ASN.1 structure. This can allow padding bytes to be removed and garbage data added to forge a signature when a low public exponent is being used. The issue has been addressed in `node-forge` version 1.3.0. There are currently no known workarounds.
<p>Publish Date: 2022-03-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24772>CVE-2022-24772</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24772">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24772</a></p>
<p>Release Date: 2022-03-18</p>
<p>Fix Resolution: node-forge - 1.3.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-24772 (High) detected in node-forge-0.10.0.tgz - ## CVE-2022-24772 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-forge-0.10.0.tgz</b></p></summary>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz</a></p>
<p>Path to dependency file: /APM-Start/package.json</p>
<p>Path to vulnerable library: /APM-Start/node_modules/node-forge/package.json,/APM-Final/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.1102.3.tgz (Root Library)
- webpack-dev-server-3.11.2.tgz
- selfsigned-1.10.8.tgz
- :x: **node-forge-0.10.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Forge (also called `node-forge`) is a native implementation of Transport Layer Security in JavaScript. Prior to version 1.3.0, RSA PKCS#1 v1.5 signature verification code does not check for tailing garbage bytes after decoding a `DigestInfo` ASN.1 structure. This can allow padding bytes to be removed and garbage data added to forge a signature when a low public exponent is being used. The issue has been addressed in `node-forge` version 1.3.0. There are currently no known workarounds.
<p>Publish Date: 2022-03-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24772>CVE-2022-24772</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24772">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24772</a></p>
<p>Release Date: 2022-03-18</p>
<p>Fix Resolution: node-forge - 1.3.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in node forge tgz cve high severity vulnerability vulnerable library node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file apm start package json path to vulnerable library apm start node modules node forge package json apm final node modules node forge package json dependency hierarchy build angular tgz root library webpack dev server tgz selfsigned tgz x node forge tgz vulnerable library found in base branch main vulnerability details forge also called node forge is a native implementation of transport layer security in javascript prior to version rsa pkcs signature verification code does not check for tailing garbage bytes after decoding a digestinfo asn structure this can allow padding bytes to be removed and garbage data added to forge a signature when a low public exponent is being used the issue has been addressed in node forge version there are currently no known workarounds publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution node forge step up your open source security game with whitesource | 0 |
230,990 | 18,727,893,749 | IssuesEvent | 2021-11-03 18:10:30 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | [test-failed]: Chrome UI Functional Tests1.test/functional/apps/dashboard/dashboard_listing·ts - dashboard app using legacy data dashboard listing page search by title loads a dashboard if title matches | Team:Presentation failed-test test-cloud | **Version: 7.13.0**
**Class: Chrome UI Functional Tests1.test/functional/apps/dashboard/dashboard_listing·ts**
**Stack Trace:**
```
Error: expected true to equal false
at Assertion.assert (node_modules/@kbn/expect/expect.js:100:11)
at Assertion.equal (node_modules/@kbn/expect/expect.js:227:8)
at Context.<anonymous> (test/functional/apps/dashboard/dashboard_listing.ts:126:43)
at runMicrotasks (<anonymous>)
at processTicksAndRejections (internal/process/task_queues.js:93:5)
at Object.apply (node_modules/@kbn/test/src/functional_test_runner/lib/mocha/wrap_function.js:73:16)
```
**Other test failures:**
- dashboard app using legacy data dashboard listing page search by title title match is case insensitive
- dashboard app using legacy data dashboard listing page search by title preloads search filter bar when there is no match
_Test Report: https://internal-ci.elastic.co/view/Stack%20Tests/job/elastic+estf-cloud-kibana-tests/1685/testReport/_ | 2.0 | [test-failed]: Chrome UI Functional Tests1.test/functional/apps/dashboard/dashboard_listing·ts - dashboard app using legacy data dashboard listing page search by title loads a dashboard if title matches - **Version: 7.13.0**
**Class: Chrome UI Functional Tests1.test/functional/apps/dashboard/dashboard_listing·ts**
**Stack Trace:**
```
Error: expected true to equal false
at Assertion.assert (node_modules/@kbn/expect/expect.js:100:11)
at Assertion.equal (node_modules/@kbn/expect/expect.js:227:8)
at Context.<anonymous> (test/functional/apps/dashboard/dashboard_listing.ts:126:43)
at runMicrotasks (<anonymous>)
at processTicksAndRejections (internal/process/task_queues.js:93:5)
at Object.apply (node_modules/@kbn/test/src/functional_test_runner/lib/mocha/wrap_function.js:73:16)
```
**Other test failures:**
- dashboard app using legacy data dashboard listing page search by title title match is case insensitive
- dashboard app using legacy data dashboard listing page search by title preloads search filter bar when there is no match
_Test Report: https://internal-ci.elastic.co/view/Stack%20Tests/job/elastic+estf-cloud-kibana-tests/1685/testReport/_ | non_priority | chrome ui functional test functional apps dashboard dashboard listing·ts dashboard app using legacy data dashboard listing page search by title loads a dashboard if title matches version class chrome ui functional test functional apps dashboard dashboard listing·ts stack trace error expected true to equal false at assertion assert node modules kbn expect expect js at assertion equal node modules kbn expect expect js at context test functional apps dashboard dashboard listing ts at runmicrotasks at processticksandrejections internal process task queues js at object apply node modules kbn test src functional test runner lib mocha wrap function js other test failures dashboard app using legacy data dashboard listing page search by title title match is case insensitive dashboard app using legacy data dashboard listing page search by title preloads search filter bar when there is no match test report | 0 |
236,048 | 19,488,835,309 | IssuesEvent | 2021-12-26 23:29:31 | MitchellTFord/discord-bot | https://api.github.com/repos/MitchellTFord/discord-bot | closed | Add JaCoCo for viewing test coverage | good first issue testing | [JaCoCo Java Code Coverage Library](https://www.eclemma.org/jacoco/)
Acceptance Criteria
* The Gradle task `test` should automatically generate an HTML code coverage report
* `README.md` should be updated with instructions on how to view coverage reports | 1.0 | Add JaCoCo for viewing test coverage - [JaCoCo Java Code Coverage Library](https://www.eclemma.org/jacoco/)
Acceptance Criteria
* The Gradle task `test` should automatically generate an HTML code coverage report
* `README.md` should be updated with instructions on how to view coverage reports | non_priority | add jacoco for viewing test coverage acceptance criteria the gradle task test should automatically generate an html code coverage report readme md should be updated with instructions on how to view coverage reports | 0 |
82,289 | 23,730,367,872 | IssuesEvent | 2022-08-31 00:48:55 | microsoft/ApplicationInsights-Python | https://api.github.com/repos/microsoft/ApplicationInsights-Python | opened | Create README in distro subfolder, change README in root folder to be generic | build/infrastucture | We want a README in the distro folder so that users can see it appear on Pypi for that specific project.
We want a README in the root folder to be the first thing users see when they come to this repo, so it should contain information that is generic (perhaps link to the other packages). | 1.0 | Create README in distro subfolder, change README in root folder to be generic - We want a README in the distro folder so that users can see it appear on Pypi for that specific project.
We want a README in the root folder to be the first thing users see when they come to this repo, so it should contain information that is generic (perhaps link to the other packages). | non_priority | create readme in distro subfolder change readme in root folder to be generic we want a readme in the distro folder so that users can see it appear on pypi for that specific project we want a readme in the root folder to be the first thing users see when they come to this repo so it should contain information that is generic perhaps link to the other packages | 0 |
253,219 | 21,664,127,842 | IssuesEvent | 2022-05-07 00:24:41 | twitter-dart/twitter-api-v2 | https://api.github.com/repos/twitter-dart/twitter-api-v2 | closed | Add `codecov.yml` | test | <!-- When reporting a feature, please read this complete template and fill all the questions in order to get a better response -->
# 1. Problem to solve
<!-- Which problem would be solved with this feature? -->
```yaml
ignore:
- "**/*.freezed.dart"
- "**/*.g.dart"
```
# 2. Proposal
<!-- What do you propose as a solution? Add as much information as you can! -->
# 3. More information
<!-- Do you have any other useful information about this feature report? Please write it down here -->
<!-- Possible helpful information: references to other sites/repositories -->
<!-- Are you interested in working on a PR for this? -->
| 1.0 | Add `codecov.yml` - <!-- When reporting a feature, please read this complete template and fill all the questions in order to get a better response -->
# 1. Problem to solve
<!-- Which problem would be solved with this feature? -->
```yaml
ignore:
- "**/*.freezed.dart"
- "**/*.g.dart"
```
# 2. Proposal
<!-- What do you propose as a solution? Add as much information as you can! -->
# 3. More information
<!-- Do you have any other useful information about this feature report? Please write it down here -->
<!-- Possible helpful information: references to other sites/repositories -->
<!-- Are you interested in working on a PR for this? -->
| non_priority | add codecov yml problem to solve yaml ignore freezed dart g dart proposal more information | 0 |
406,689 | 27,577,600,684 | IssuesEvent | 2023-03-08 14:08:21 | Azure-Samples/modern-data-warehouse-dataops | https://api.github.com/repos/Azure-Samples/modern-data-warehouse-dataops | closed | Additions to the ReadMe.md file | documentation single-tech: synapse | **Goal**
Add relevant information on the ReadMe file
**DoD**
- Add a note on the source data not being on a star schema. For simplicity reasons the sample is using NYC Taxi data.
- Add note in partitioning
- Add all changes done during the hack
- Refer that the triggers starts automatically
- ACL limitation
- Partitioning (physical/logical)
- Add to the clean-up instructions: after deletion of resource group make sure you purge the keyvault with `az keyvault purge --name <keyvault-name>`
**Optional**
- consider pointing out that the ACLs are set via Spark Notebooks but this might not be optimal | 1.0 | Additions to the ReadMe.md file - **Goal**
Add relevant information on the ReadMe file
**DoD**
- Add a note on the source data not being on a star schema. For simplicity reasons the sample is using NYC Taxi data.
- Add note in partitioning
- Add all changes done during the hack
- Refer that the triggers starts automatically
- ACL limitation
- Partitioning (physical/logical)
- Add to the clean-up instructions: after deletion of resource group make sure you purge the keyvault with `az keyvault purge --name <keyvault-name>`
**Optional**
- consider pointing out that the ACLs are set via Spark Notebooks but this might not be optimal | non_priority | additions to the readme md file goal add relevant information on the readme file dod add a note on the source data not being on a star schema for simplicity reasons the sample is using nyc taxi data add note in partitioning add all changes done during the hack refer that the triggers starts automatically acl limitation partitioning physical logical add to the clean up instructions after deletion of resource group make sure you purge the keyvault with az keyvault purge name optional consider pointing out that the acls are set via spark notebooks but this might not be optimal | 0 |
165,462 | 26,175,317,423 | IssuesEvent | 2023-01-02 09:00:54 | spacemeshos/pm | https://api.github.com/repos/spacemeshos/pm | closed | Redundant PoET registration | design | PoET servers are a potential single-point-of-failure. There are many scenarios where PoETs can be attacked and possibly fail. We want to establish the PoET <-> Node interface in such a way that a Node can register with multiple PoET servers. | 1.0 | Redundant PoET registration - PoET servers are a potential single-point-of-failure. There are many scenarios where PoETs can be attacked and possibly fail. We want to establish the PoET <-> Node interface in such a way that a Node can register with multiple PoET servers. | non_priority | redundant poet registration poet servers are a potential single point of failure there are many scenarios where poets can be attacked and possibly fail we want to establish the poet node interface in such a way that a node can register with multiple poet servers | 0 |
226,846 | 18,044,748,712 | IssuesEvent | 2021-09-18 17:48:26 | zkSNACKs/WalletWasabi | https://api.github.com/repos/zkSNACKs/WalletWasabi | closed | [Fluent] Priv/Pub key different icon | UI ww2 testing | In for example the `Wallet Info` Dialog, the private and public keys have the same icon.
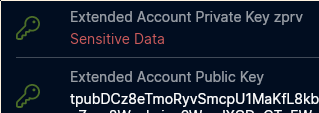
It would be better to somehow differentiate those two on the icon level. | 1.0 | [Fluent] Priv/Pub key different icon - In for example the `Wallet Info` Dialog, the private and public keys have the same icon.
It would be better to somehow differentiate those two on the icon level. | non_priority | priv pub key different icon in for example the wallet info dialog the private and public keys have the same icon it would be better to somehow differentiate those two on the icon level | 0 |
348,268 | 24,910,132,184 | IssuesEvent | 2022-10-29 19:05:17 | 2M4U/2m4u | https://api.github.com/repos/2M4U/2m4u | closed | Missing Code_Of_Conduct.md | documentation hacktober-approved | Hey, I think you are missing the code of conduct file, which is an important part of all the Hacktoberfest repo. If you think you want to add it, I could help you with this task... I would add the code of conduct guidelines given under the original Hacktoberfest repo. | 1.0 | Missing Code_Of_Conduct.md - Hey, I think you are missing the code of conduct file, which is an important part of all the Hacktoberfest repo. If you think you want to add it, I could help you with this task... I would add the code of conduct guidelines given under the original Hacktoberfest repo. | non_priority | missing code of conduct md hey i think you are missing the code of conduct file which is an important part of all the hacktoberfest repo if you think you want to add it i could help you with this task i would add the code of conduct guidelines given under the original hacktoberfest repo | 0 |
41,001 | 6,886,988,441 | IssuesEvent | 2017-11-21 21:32:24 | USDA-FSA/fsa-design-system | https://api.github.com/repos/USDA-FSA/fsa-design-system | opened | Documentation: Update broken or ill-formatted links | BUG Category: Documentation P2 Type: Guide |
- Update broken Color Page link on[ Application Guides page at bottom](http://usda-fsa.github.io/fsa-design-system/guides/applications/)
- Several dynamic links are "//" in the URL which can cause problems is certain browsers. | 1.0 | Documentation: Update broken or ill-formatted links -
- Update broken Color Page link on[ Application Guides page at bottom](http://usda-fsa.github.io/fsa-design-system/guides/applications/)
- Several dynamic links are "//" in the URL which can cause problems is certain browsers. | non_priority | documentation update broken or ill formatted links update broken color page link on several dynamic links are in the url which can cause problems is certain browsers | 0 |
299,065 | 25,877,403,274 | IssuesEvent | 2022-12-14 08:55:59 | allure-framework/allure-python | https://api.github.com/repos/allure-framework/allure-python | closed | @pytest.allure.link not adding link in report | type:bug theme:pytest | #### I'm submitting a ...
- [x] bug report
- [ ] feature request
- [ ] support request => Please do not submit support request here, see note at the top of this template.
#### What is the current behavior?
Unable to get Links in the allure report using `@pytest.allure.link() `or `@allure.link`
However using `allure.dynamic.link("www.google.com",name='Click me')` inside the test works
#### If the current behavior is a bug, please provide the steps to reproduce and if possible a minimal demo of the problem
`@pytest.allure.link("www.google.com")` creates a LINKS header in report but value is not displayed there.
#### What is the expected behavior?
The correct given link should be displayed in the report
#### Please tell us about your environment:
`{'Python': '2.7.15', 'Platform': 'Darwin-17.4.0-x86_64-i386-64bit', 'Packages': {'py': '1.5.4', 'pytest': '3.7.0', 'pluggy': '0.7.1'}, 'Plugins': {'forked': '0.2', 'html': '1.19.0', 'xdist': '1.22.5', 'allure-pytest': '2.5.0', 'metadata': '1.7.0'}}`
| 1.0 | @pytest.allure.link not adding link in report - #### I'm submitting a ...
- [x] bug report
- [ ] feature request
- [ ] support request => Please do not submit support request here, see note at the top of this template.
#### What is the current behavior?
Unable to get Links in the allure report using `@pytest.allure.link() `or `@allure.link`
However using `allure.dynamic.link("www.google.com",name='Click me')` inside the test works
#### If the current behavior is a bug, please provide the steps to reproduce and if possible a minimal demo of the problem
`@pytest.allure.link("www.google.com")` creates a LINKS header in report but value is not displayed there.
#### What is the expected behavior?
The correct given link should be displayed in the report
#### Please tell us about your environment:
`{'Python': '2.7.15', 'Platform': 'Darwin-17.4.0-x86_64-i386-64bit', 'Packages': {'py': '1.5.4', 'pytest': '3.7.0', 'pluggy': '0.7.1'}, 'Plugins': {'forked': '0.2', 'html': '1.19.0', 'xdist': '1.22.5', 'allure-pytest': '2.5.0', 'metadata': '1.7.0'}}`
| non_priority | pytest allure link not adding link in report i m submitting a bug report feature request support request please do not submit support request here see note at the top of this template what is the current behavior unable to get links in the allure report using pytest allure link or allure link however using allure dynamic link me inside the test works if the current behavior is a bug please provide the steps to reproduce and if possible a minimal demo of the problem pytest allure link creates a links header in report but value is not displayed there what is the expected behavior the correct given link should be displayed in the report please tell us about your environment python platform darwin packages py pytest pluggy plugins forked html xdist allure pytest metadata | 0 |
290,364 | 25,051,459,896 | IssuesEvent | 2022-11-05 23:38:38 | FuelLabs/sway | https://api.github.com/repos/FuelLabs/sway | closed | Reenable the `u128_root_test` that was disabled in #3181 | lib: std testing | https://github.com/FuelLabs/sway/pull/3181 disables `u128_root_test` because the test was running out of gas with the new gas schedule in `fuel-core 0.13`. We can increase the gas limit but I think a better approach would be to figure out a better implementation of the `sqrt` function. I think the division operation takes too much gas now so we can change some of the divisions by 2 to shift rights. | 1.0 | Reenable the `u128_root_test` that was disabled in #3181 - https://github.com/FuelLabs/sway/pull/3181 disables `u128_root_test` because the test was running out of gas with the new gas schedule in `fuel-core 0.13`. We can increase the gas limit but I think a better approach would be to figure out a better implementation of the `sqrt` function. I think the division operation takes too much gas now so we can change some of the divisions by 2 to shift rights. | non_priority | reenable the root test that was disabled in disables root test because the test was running out of gas with the new gas schedule in fuel core we can increase the gas limit but i think a better approach would be to figure out a better implementation of the sqrt function i think the division operation takes too much gas now so we can change some of the divisions by to shift rights | 0 |
215,980 | 24,205,266,202 | IssuesEvent | 2022-09-25 05:48:22 | ignatandrei/WFH_Resources | https://api.github.com/repos/ignatandrei/WFH_Resources | closed | CVE-2021-3664 (Medium) detected in url-parse-1.4.7.tgz - autoclosed | security vulnerability | ## CVE-2021-3664 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.4.7.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz</a></p>
<p>Path to dependency file: /WFHResourcesApp/package.json</p>
<p>Path to vulnerable library: /WFHResourcesApp/node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.900.6.tgz (Root Library)
- webpack-dev-server-3.9.0.tgz
- sockjs-client-1.4.0.tgz
- :x: **url-parse-1.4.7.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
url-parse is vulnerable to URL Redirection to Untrusted Site
<p>Publish Date: 2021-07-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3664>CVE-2021-3664</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-3664">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-3664</a></p>
<p>Release Date: 2021-07-26</p>
<p>Fix Resolution (url-parse): 1.5.2</p>
<p>Direct dependency fix Resolution (@angular-devkit/build-angular): 0.900.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-3664 (Medium) detected in url-parse-1.4.7.tgz - autoclosed - ## CVE-2021-3664 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.4.7.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz</a></p>
<p>Path to dependency file: /WFHResourcesApp/package.json</p>
<p>Path to vulnerable library: /WFHResourcesApp/node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.900.6.tgz (Root Library)
- webpack-dev-server-3.9.0.tgz
- sockjs-client-1.4.0.tgz
- :x: **url-parse-1.4.7.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
url-parse is vulnerable to URL Redirection to Untrusted Site
<p>Publish Date: 2021-07-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3664>CVE-2021-3664</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-3664">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-3664</a></p>
<p>Release Date: 2021-07-26</p>
<p>Fix Resolution (url-parse): 1.5.2</p>
<p>Direct dependency fix Resolution (@angular-devkit/build-angular): 0.900.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in url parse tgz autoclosed cve medium severity vulnerability vulnerable library url parse tgz small footprint url parser that works seamlessly across node js and browser environments library home page a href path to dependency file wfhresourcesapp package json path to vulnerable library wfhresourcesapp node modules url parse package json dependency hierarchy build angular tgz root library webpack dev server tgz sockjs client tgz x url parse tgz vulnerable library found in base branch master vulnerability details url parse is vulnerable to url redirection to untrusted site publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution url parse direct dependency fix resolution angular devkit build angular step up your open source security game with mend | 0 |
15,643 | 5,162,373,652 | IssuesEvent | 2017-01-17 00:19:30 | neuroailab/tfutils | https://api.github.com/repos/neuroailab/tfutils | reopened | Split up Saver and Loader?? | clean up code | Proposed split: DBInterface as a base class that sets up host, collection etc and has a `get_record`method, with Saver and Loader inheriting from this class. See [base.py in clean_interface branch](https://github.com/neuroailab/tfutils/blob/clean_interface/tfutils/base.py) for an example.
Benefits:
- Clean division between loading processes and saving processes with a clear logic where load and save parameters are going and which methods are for loading and which are for saving.
- Saver and Loader do not seem to interact in a deep way, so their combination is not motivated.
- The not nice setting of `self.` parameters in 172-192 is resolved. | 1.0 | Split up Saver and Loader?? - Proposed split: DBInterface as a base class that sets up host, collection etc and has a `get_record`method, with Saver and Loader inheriting from this class. See [base.py in clean_interface branch](https://github.com/neuroailab/tfutils/blob/clean_interface/tfutils/base.py) for an example.
Benefits:
- Clean division between loading processes and saving processes with a clear logic where load and save parameters are going and which methods are for loading and which are for saving.
- Saver and Loader do not seem to interact in a deep way, so their combination is not motivated.
- The not nice setting of `self.` parameters in 172-192 is resolved. | non_priority | split up saver and loader proposed split dbinterface as a base class that sets up host collection etc and has a get record method with saver and loader inheriting from this class see for an example benefits clean division between loading processes and saving processes with a clear logic where load and save parameters are going and which methods are for loading and which are for saving saver and loader do not seem to interact in a deep way so their combination is not motivated the not nice setting of self parameters in is resolved | 0 |
95,301 | 8,555,451,749 | IssuesEvent | 2018-11-08 10:04:44 | humera987/FXLabs-Test-Automation | https://api.github.com/repos/humera987/FXLabs-Test-Automation | reopened | testing8 : ApiV1OrgsOrgidOrgUserOrguseridGetPathParamOrguseridNullValue | testing8 testing8 | Project : testing8
Job : UAT
Env : UAT
Region : US_WEST_3
Result : fail
Status Code : 500
Headers : {}
Endpoint : http://13.56.210.25/api/v1/api/v1/orgs/{orgId}/org-user/null
Request :
Response :
Not enough variable values available to expand 'orgId'
Logs :
Assertion [@StatusCode != 401] resolved-to [500 != 401] result [Passed]Assertion [@StatusCode != 500] resolved-to [500 != 500] result [Failed]Assertion [@StatusCode != 404] resolved-to [500 != 404] result [Passed]Assertion [@StatusCode != 200] resolved-to [500 != 200] result [Passed]
--- FX Bot --- | 2.0 | testing8 : ApiV1OrgsOrgidOrgUserOrguseridGetPathParamOrguseridNullValue - Project : testing8
Job : UAT
Env : UAT
Region : US_WEST_3
Result : fail
Status Code : 500
Headers : {}
Endpoint : http://13.56.210.25/api/v1/api/v1/orgs/{orgId}/org-user/null
Request :
Response :
Not enough variable values available to expand 'orgId'
Logs :
Assertion [@StatusCode != 401] resolved-to [500 != 401] result [Passed]Assertion [@StatusCode != 500] resolved-to [500 != 500] result [Failed]Assertion [@StatusCode != 404] resolved-to [500 != 404] result [Passed]Assertion [@StatusCode != 200] resolved-to [500 != 200] result [Passed]
--- FX Bot --- | non_priority | project job uat env uat region us west result fail status code headers endpoint request response not enough variable values available to expand orgid logs assertion resolved to result assertion resolved to result assertion resolved to result assertion resolved to result fx bot | 0 |
12,022 | 7,622,954,175 | IssuesEvent | 2018-05-03 13:47:15 | LibreHealthIO/lh-ehr | https://api.github.com/repos/LibreHealthIO/lh-ehr | closed | Setup Script (web version) improvement | Quick Win Usability bug enhancement | The setup script needs general improvement. Some recent stuff from Matrix on openemr might be good, but we also need to make sure that it does not update the sqlconf.php file as "Installed" until AFTER it's actually successful.
Also need to make sure that SQL errors during setup are trapped and not silently skipped over to be found sometime later by the user when they try and use a part of the install.
| True | Setup Script (web version) improvement - The setup script needs general improvement. Some recent stuff from Matrix on openemr might be good, but we also need to make sure that it does not update the sqlconf.php file as "Installed" until AFTER it's actually successful.
Also need to make sure that SQL errors during setup are trapped and not silently skipped over to be found sometime later by the user when they try and use a part of the install.
| non_priority | setup script web version improvement the setup script needs general improvement some recent stuff from matrix on openemr might be good but we also need to make sure that it does not update the sqlconf php file as installed until after it s actually successful also need to make sure that sql errors during setup are trapped and not silently skipped over to be found sometime later by the user when they try and use a part of the install | 0 |
231,460 | 25,499,437,886 | IssuesEvent | 2022-11-28 01:42:12 | DevOpsOpenHack/devopsohteam4 | https://api.github.com/repos/DevOpsOpenHack/devopsohteam4 | closed | github.com/denisenkom/go-mssqldb-v0.10.0: 6 vulnerabilities (highest severity is: 7.5) - autoclosed | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/denisenkom/go-mssqldb-v0.10.0</b></p></summary>
<p></p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/DevOpsOpenHack/devopsohteam4/commit/0b34798e47770cd5cdb86f04f918575251d92f0c">0b34798e47770cd5cdb86f04f918575251d92f0c</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (github.com/denisenkom/go-mssqldb-v0.10.0 version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-27191](https://www.mend.io/vulnerability-database/CVE-2022-27191) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692 | Transitive | N/A* | ❌ |
| [CVE-2020-9283](https://www.mend.io/vulnerability-database/CVE-2020-9283) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692 | Transitive | N/A* | ❌ |
| [CVE-2020-29652](https://www.mend.io/vulnerability-database/CVE-2020-29652) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692 | Transitive | N/A* | ❌ |
| [CVE-2021-43565](https://www.mend.io/vulnerability-database/CVE-2021-43565) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692 | Transitive | N/A* | ❌ |
| [CVE-2020-7919](https://www.mend.io/vulnerability-database/CVE-2020-7919) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692 | Transitive | N/A* | ❌ |
| [CVE-2019-11841](https://www.mend.io/vulnerability-database/CVE-2019-11841) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692 | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-27191</summary>
### Vulnerable Library - <b>github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692</b></p>
<p>[mirror] Go supplementary cryptography libraries</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip">https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip</a></p>
<p>
Dependency Hierarchy:
- github.com/denisenkom/go-mssqldb-v0.10.0 (Root Library)
- :x: **github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/DevOpsOpenHack/devopsohteam4/commit/0b34798e47770cd5cdb86f04f918575251d92f0c">0b34798e47770cd5cdb86f04f918575251d92f0c</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The golang.org/x/crypto/ssh package before 0.0.0-20220314234659-1baeb1ce4c0b for Go allows an attacker to crash a server in certain circumstances involving AddHostKey.
<p>Publish Date: 2022-03-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-27191>CVE-2022-27191</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2022-27191">https://nvd.nist.gov/vuln/detail/CVE-2022-27191</a></p>
<p>Release Date: 2022-03-18</p>
<p>Fix Resolution: golang-golang-x-crypto-dev - 1:0.0~git20220315.3147a52-1;golang-go.crypto-dev - 1:0.0~git20220315.3147a52-1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9283</summary>
### Vulnerable Library - <b>github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692</b></p>
<p>[mirror] Go supplementary cryptography libraries</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip">https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip</a></p>
<p>
Dependency Hierarchy:
- github.com/denisenkom/go-mssqldb-v0.10.0 (Root Library)
- :x: **github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/DevOpsOpenHack/devopsohteam4/commit/0b34798e47770cd5cdb86f04f918575251d92f0c">0b34798e47770cd5cdb86f04f918575251d92f0c</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
golang.org/x/crypto before v0.0.0-20200220183623-bac4c82f6975 for Go allows a panic during signature verification in the golang.org/x/crypto/ssh package. A client can attack an SSH server that accepts public keys. Also, a server can attack any SSH client.
<p>Publish Date: 2020-02-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-9283>CVE-2020-9283</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9283">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9283</a></p>
<p>Release Date: 2020-02-20</p>
<p>Fix Resolution: github.com/golang/crypto - bac4c82f69751a6dd76e702d54b3ceb88adab236</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-29652</summary>
### Vulnerable Library - <b>github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692</b></p>
<p>[mirror] Go supplementary cryptography libraries</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip">https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip</a></p>
<p>
Dependency Hierarchy:
- github.com/denisenkom/go-mssqldb-v0.10.0 (Root Library)
- :x: **github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/DevOpsOpenHack/devopsohteam4/commit/0b34798e47770cd5cdb86f04f918575251d92f0c">0b34798e47770cd5cdb86f04f918575251d92f0c</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A nil pointer dereference in the golang.org/x/crypto/ssh component through v0.0.0-20201203163018-be400aefbc4c for Go allows remote attackers to cause a denial of service against SSH servers.
<p>Publish Date: 2020-12-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-29652>CVE-2020-29652</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://groups.google.com/g/golang-announce/c/ouZIlBimOsE?pli=1">https://groups.google.com/g/golang-announce/c/ouZIlBimOsE?pli=1</a></p>
<p>Release Date: 2020-12-17</p>
<p>Fix Resolution: v0.0.0-20201216223049-8b5274cf687f</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-43565</summary>
### Vulnerable Library - <b>github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692</b></p>
<p>[mirror] Go supplementary cryptography libraries</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip">https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip</a></p>
<p>
Dependency Hierarchy:
- github.com/denisenkom/go-mssqldb-v0.10.0 (Root Library)
- :x: **github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/DevOpsOpenHack/devopsohteam4/commit/0b34798e47770cd5cdb86f04f918575251d92f0c">0b34798e47770cd5cdb86f04f918575251d92f0c</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The x/crypto/ssh package before 0.0.0-20211202192323-5770296d904e of golang.org/x/crypto allows an attacker to panic an SSH server.
<p>Publish Date: 2022-09-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-43565>CVE-2021-43565</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-43565">https://nvd.nist.gov/vuln/detail/CVE-2021-43565</a></p>
<p>Release Date: 2021-11-10</p>
<p>Fix Resolution: golang-golang-x-crypto-dev - 1:0.0~git20211202.5770296-1;golang-go.crypto-dev - 1:0.0~git20211202.5770296-1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7919</summary>
### Vulnerable Library - <b>github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692</b></p>
<p>[mirror] Go supplementary cryptography libraries</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip">https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip</a></p>
<p>
Dependency Hierarchy:
- github.com/denisenkom/go-mssqldb-v0.10.0 (Root Library)
- :x: **github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/DevOpsOpenHack/devopsohteam4/commit/0b34798e47770cd5cdb86f04f918575251d92f0c">0b34798e47770cd5cdb86f04f918575251d92f0c</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Go before 1.12.16 and 1.13.x before 1.13.7 (and the crypto/cryptobyte package before 0.0.0-20200124225646-8b5121be2f68 for Go) allows attacks on clients (resulting in a panic) via a malformed X.509 certificate.
<p>Publish Date: 2020-03-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-7919>CVE-2020-7919</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7919">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7919</a></p>
<p>Release Date: 2020-03-16</p>
<p>Fix Resolution: go - 1.12.16,1.13.7;crypto - v0.0.0-20200128174031-69ecbb4d6d5d</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-11841</summary>
### Vulnerable Library - <b>github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692</b></p>
<p>[mirror] Go supplementary cryptography libraries</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip">https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip</a></p>
<p>
Dependency Hierarchy:
- github.com/denisenkom/go-mssqldb-v0.10.0 (Root Library)
- :x: **github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/DevOpsOpenHack/devopsohteam4/commit/0b34798e47770cd5cdb86f04f918575251d92f0c">0b34798e47770cd5cdb86f04f918575251d92f0c</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A message-forgery issue was discovered in crypto/openpgp/clearsign/clearsign.go in supplementary Go cryptography libraries 2019-03-25. According to the OpenPGP Message Format specification in RFC 4880 chapter 7, a cleartext signed message can contain one or more optional "Hash" Armor Headers. The "Hash" Armor Header specifies the message digest algorithm(s) used for the signature. However, the Go clearsign package ignores the value of this header, which allows an attacker to spoof it. Consequently, an attacker can lead a victim to believe the signature was generated using a different message digest algorithm than what was actually used. Moreover, since the library skips Armor Header parsing in general, an attacker can not only embed arbitrary Armor Headers, but also prepend arbitrary text to cleartext messages without invalidating the signatures.
<p>Publish Date: 2019-05-22
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-11841>CVE-2019-11841</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2019-11841">https://nvd.nist.gov/vuln/detail/CVE-2019-11841</a></p>
<p>Release Date: 2019-05-22</p>
<p>Fix Resolution: golang-golang-x-crypto-dev - 1:0.0~git20200221.2aa609c-1,1:0.0~git20170407.0.55a552f+REALLY.0.0~git20161012.0.5f31782-1+deb8u1,1:0.0~git20200221.2aa609c-1;golang-go.crypto-dev - 1:0.0~git20170407.0.55a552f+REALLY.0.0~git20161012.0.5f31782-1+deb8u1,1:0.0~git20200221.2aa609c-1,1:0.0~git20200221.2aa609c-1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | True | github.com/denisenkom/go-mssqldb-v0.10.0: 6 vulnerabilities (highest severity is: 7.5) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/denisenkom/go-mssqldb-v0.10.0</b></p></summary>
<p></p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/DevOpsOpenHack/devopsohteam4/commit/0b34798e47770cd5cdb86f04f918575251d92f0c">0b34798e47770cd5cdb86f04f918575251d92f0c</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (github.com/denisenkom/go-mssqldb-v0.10.0 version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-27191](https://www.mend.io/vulnerability-database/CVE-2022-27191) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692 | Transitive | N/A* | ❌ |
| [CVE-2020-9283](https://www.mend.io/vulnerability-database/CVE-2020-9283) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692 | Transitive | N/A* | ❌ |
| [CVE-2020-29652](https://www.mend.io/vulnerability-database/CVE-2020-29652) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692 | Transitive | N/A* | ❌ |
| [CVE-2021-43565](https://www.mend.io/vulnerability-database/CVE-2021-43565) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692 | Transitive | N/A* | ❌ |
| [CVE-2020-7919](https://www.mend.io/vulnerability-database/CVE-2020-7919) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692 | Transitive | N/A* | ❌ |
| [CVE-2019-11841](https://www.mend.io/vulnerability-database/CVE-2019-11841) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692 | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-27191</summary>
### Vulnerable Library - <b>github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692</b></p>
<p>[mirror] Go supplementary cryptography libraries</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip">https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip</a></p>
<p>
Dependency Hierarchy:
- github.com/denisenkom/go-mssqldb-v0.10.0 (Root Library)
- :x: **github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/DevOpsOpenHack/devopsohteam4/commit/0b34798e47770cd5cdb86f04f918575251d92f0c">0b34798e47770cd5cdb86f04f918575251d92f0c</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The golang.org/x/crypto/ssh package before 0.0.0-20220314234659-1baeb1ce4c0b for Go allows an attacker to crash a server in certain circumstances involving AddHostKey.
<p>Publish Date: 2022-03-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-27191>CVE-2022-27191</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2022-27191">https://nvd.nist.gov/vuln/detail/CVE-2022-27191</a></p>
<p>Release Date: 2022-03-18</p>
<p>Fix Resolution: golang-golang-x-crypto-dev - 1:0.0~git20220315.3147a52-1;golang-go.crypto-dev - 1:0.0~git20220315.3147a52-1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9283</summary>
### Vulnerable Library - <b>github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692</b></p>
<p>[mirror] Go supplementary cryptography libraries</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip">https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip</a></p>
<p>
Dependency Hierarchy:
- github.com/denisenkom/go-mssqldb-v0.10.0 (Root Library)
- :x: **github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/DevOpsOpenHack/devopsohteam4/commit/0b34798e47770cd5cdb86f04f918575251d92f0c">0b34798e47770cd5cdb86f04f918575251d92f0c</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
golang.org/x/crypto before v0.0.0-20200220183623-bac4c82f6975 for Go allows a panic during signature verification in the golang.org/x/crypto/ssh package. A client can attack an SSH server that accepts public keys. Also, a server can attack any SSH client.
<p>Publish Date: 2020-02-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-9283>CVE-2020-9283</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9283">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9283</a></p>
<p>Release Date: 2020-02-20</p>
<p>Fix Resolution: github.com/golang/crypto - bac4c82f69751a6dd76e702d54b3ceb88adab236</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-29652</summary>
### Vulnerable Library - <b>github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692</b></p>
<p>[mirror] Go supplementary cryptography libraries</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip">https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip</a></p>
<p>
Dependency Hierarchy:
- github.com/denisenkom/go-mssqldb-v0.10.0 (Root Library)
- :x: **github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/DevOpsOpenHack/devopsohteam4/commit/0b34798e47770cd5cdb86f04f918575251d92f0c">0b34798e47770cd5cdb86f04f918575251d92f0c</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A nil pointer dereference in the golang.org/x/crypto/ssh component through v0.0.0-20201203163018-be400aefbc4c for Go allows remote attackers to cause a denial of service against SSH servers.
<p>Publish Date: 2020-12-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-29652>CVE-2020-29652</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://groups.google.com/g/golang-announce/c/ouZIlBimOsE?pli=1">https://groups.google.com/g/golang-announce/c/ouZIlBimOsE?pli=1</a></p>
<p>Release Date: 2020-12-17</p>
<p>Fix Resolution: v0.0.0-20201216223049-8b5274cf687f</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-43565</summary>
### Vulnerable Library - <b>github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692</b></p>
<p>[mirror] Go supplementary cryptography libraries</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip">https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip</a></p>
<p>
Dependency Hierarchy:
- github.com/denisenkom/go-mssqldb-v0.10.0 (Root Library)
- :x: **github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/DevOpsOpenHack/devopsohteam4/commit/0b34798e47770cd5cdb86f04f918575251d92f0c">0b34798e47770cd5cdb86f04f918575251d92f0c</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The x/crypto/ssh package before 0.0.0-20211202192323-5770296d904e of golang.org/x/crypto allows an attacker to panic an SSH server.
<p>Publish Date: 2022-09-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-43565>CVE-2021-43565</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-43565">https://nvd.nist.gov/vuln/detail/CVE-2021-43565</a></p>
<p>Release Date: 2021-11-10</p>
<p>Fix Resolution: golang-golang-x-crypto-dev - 1:0.0~git20211202.5770296-1;golang-go.crypto-dev - 1:0.0~git20211202.5770296-1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7919</summary>
### Vulnerable Library - <b>github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692</b></p>
<p>[mirror] Go supplementary cryptography libraries</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip">https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip</a></p>
<p>
Dependency Hierarchy:
- github.com/denisenkom/go-mssqldb-v0.10.0 (Root Library)
- :x: **github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/DevOpsOpenHack/devopsohteam4/commit/0b34798e47770cd5cdb86f04f918575251d92f0c">0b34798e47770cd5cdb86f04f918575251d92f0c</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Go before 1.12.16 and 1.13.x before 1.13.7 (and the crypto/cryptobyte package before 0.0.0-20200124225646-8b5121be2f68 for Go) allows attacks on clients (resulting in a panic) via a malformed X.509 certificate.
<p>Publish Date: 2020-03-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-7919>CVE-2020-7919</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7919">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7919</a></p>
<p>Release Date: 2020-03-16</p>
<p>Fix Resolution: go - 1.12.16,1.13.7;crypto - v0.0.0-20200128174031-69ecbb4d6d5d</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-11841</summary>
### Vulnerable Library - <b>github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692</b></p>
<p>[mirror] Go supplementary cryptography libraries</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip">https://proxy.golang.org/github.com/golang/crypto/@v/v0.0.0-20190403202508-8e1b8d32e692.zip</a></p>
<p>
Dependency Hierarchy:
- github.com/denisenkom/go-mssqldb-v0.10.0 (Root Library)
- :x: **github.com/golang/crypto-v0.0.0-20190403202508-8e1b8d32e692** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/DevOpsOpenHack/devopsohteam4/commit/0b34798e47770cd5cdb86f04f918575251d92f0c">0b34798e47770cd5cdb86f04f918575251d92f0c</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A message-forgery issue was discovered in crypto/openpgp/clearsign/clearsign.go in supplementary Go cryptography libraries 2019-03-25. According to the OpenPGP Message Format specification in RFC 4880 chapter 7, a cleartext signed message can contain one or more optional "Hash" Armor Headers. The "Hash" Armor Header specifies the message digest algorithm(s) used for the signature. However, the Go clearsign package ignores the value of this header, which allows an attacker to spoof it. Consequently, an attacker can lead a victim to believe the signature was generated using a different message digest algorithm than what was actually used. Moreover, since the library skips Armor Header parsing in general, an attacker can not only embed arbitrary Armor Headers, but also prepend arbitrary text to cleartext messages without invalidating the signatures.
<p>Publish Date: 2019-05-22
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-11841>CVE-2019-11841</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2019-11841">https://nvd.nist.gov/vuln/detail/CVE-2019-11841</a></p>
<p>Release Date: 2019-05-22</p>
<p>Fix Resolution: golang-golang-x-crypto-dev - 1:0.0~git20200221.2aa609c-1,1:0.0~git20170407.0.55a552f+REALLY.0.0~git20161012.0.5f31782-1+deb8u1,1:0.0~git20200221.2aa609c-1;golang-go.crypto-dev - 1:0.0~git20170407.0.55a552f+REALLY.0.0~git20161012.0.5f31782-1+deb8u1,1:0.0~git20200221.2aa609c-1,1:0.0~git20200221.2aa609c-1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | non_priority | github com denisenkom go mssqldb vulnerabilities highest severity is autoclosed vulnerable library github com denisenkom go mssqldb found in head commit a href vulnerabilities cve severity cvss dependency type fixed in github com denisenkom go mssqldb version remediation available high github com golang crypto transitive n a high github com golang crypto transitive n a high github com golang crypto transitive n a high github com golang crypto transitive n a high github com golang crypto transitive n a medium github com golang crypto transitive n a for some transitive vulnerabilities there is no version of direct dependency with a fix check the section details below to see if there is a version of transitive dependency where vulnerability is fixed details cve vulnerable library github com golang crypto go supplementary cryptography libraries library home page a href dependency hierarchy github com denisenkom go mssqldb root library x github com golang crypto vulnerable library found in head commit a href found in base branch main vulnerability details the golang org x crypto ssh package before for go allows an attacker to crash a server in certain circumstances involving addhostkey publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution golang golang x crypto dev golang go crypto dev step up your open source security game with mend cve vulnerable library github com golang crypto go supplementary cryptography libraries library home page a href dependency hierarchy github com denisenkom go mssqldb root library x github com golang crypto vulnerable library found in head commit a href found in base branch main vulnerability details golang org x crypto before for go allows a panic during signature verification in the golang org x crypto ssh package a client can attack an ssh server that accepts public keys also a server can attack any ssh client publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution github com golang crypto step up your open source security game with mend cve vulnerable library github com golang crypto go supplementary cryptography libraries library home page a href dependency hierarchy github com denisenkom go mssqldb root library x github com golang crypto vulnerable library found in head commit a href found in base branch main vulnerability details a nil pointer dereference in the golang org x crypto ssh component through for go allows remote attackers to cause a denial of service against ssh servers publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library github com golang crypto go supplementary cryptography libraries library home page a href dependency hierarchy github com denisenkom go mssqldb root library x github com golang crypto vulnerable library found in head commit a href found in base branch main vulnerability details the x crypto ssh package before of golang org x crypto allows an attacker to panic an ssh server publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution golang golang x crypto dev golang go crypto dev step up your open source security game with mend cve vulnerable library github com golang crypto go supplementary cryptography libraries library home page a href dependency hierarchy github com denisenkom go mssqldb root library x github com golang crypto vulnerable library found in head commit a href found in base branch main vulnerability details go before and x before and the crypto cryptobyte package before for go allows attacks on clients resulting in a panic via a malformed x certificate publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution go crypto step up your open source security game with mend cve vulnerable library github com golang crypto go supplementary cryptography libraries library home page a href dependency hierarchy github com denisenkom go mssqldb root library x github com golang crypto vulnerable library found in head commit a href found in base branch main vulnerability details a message forgery issue was discovered in crypto openpgp clearsign clearsign go in supplementary go cryptography libraries according to the openpgp message format specification in rfc chapter a cleartext signed message can contain one or more optional hash armor headers the hash armor header specifies the message digest algorithm s used for the signature however the go clearsign package ignores the value of this header which allows an attacker to spoof it consequently an attacker can lead a victim to believe the signature was generated using a different message digest algorithm than what was actually used moreover since the library skips armor header parsing in general an attacker can not only embed arbitrary armor headers but also prepend arbitrary text to cleartext messages without invalidating the signatures publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution golang golang x crypto dev really golang go crypto dev really step up your open source security game with mend | 0 |
19,510 | 3,461,377,537 | IssuesEvent | 2015-12-20 01:08:34 | brunobuzzi/OrbeonBridgeForGemStone | https://api.github.com/repos/brunobuzzi/OrbeonBridgeForGemStone | closed | Add Execution Application Context to Process Instances | enhancement Meta Model Redesign | Right now the only way to "share" a Process Instance among more than one Application is using roles and users.
A user has various roles of different Application and that user will have access to processes of different Applications.
BUT to define a some kind of Hierarchy is not possible. For example to a have a process at a "Top Level" Application and this process "shared" by users of others Applications, possible with users and roles. The problem is that all users of any application will have access to the Process. If we add a "execution context" to the Process instance as another level of restriction the is possible to "simulate" a hierarchy. The user has to have the role to access the Process but if the Process Instance has an "execution context" (anApplication) it also has to have a role for that application.

| 1.0 | Add Execution Application Context to Process Instances - Right now the only way to "share" a Process Instance among more than one Application is using roles and users.
A user has various roles of different Application and that user will have access to processes of different Applications.
BUT to define a some kind of Hierarchy is not possible. For example to a have a process at a "Top Level" Application and this process "shared" by users of others Applications, possible with users and roles. The problem is that all users of any application will have access to the Process. If we add a "execution context" to the Process instance as another level of restriction the is possible to "simulate" a hierarchy. The user has to have the role to access the Process but if the Process Instance has an "execution context" (anApplication) it also has to have a role for that application.

| non_priority | add execution application context to process instances right now the only way to share a process instance among more than one application is using roles and users a user has various roles of different application and that user will have access to processes of different applications but to define a some kind of hierarchy is not possible for example to a have a process at a top level application and this process shared by users of others applications possible with users and roles the problem is that all users of any application will have access to the process if we add a execution context to the process instance as another level of restriction the is possible to simulate a hierarchy the user has to have the role to access the process but if the process instance has an execution context anapplication it also has to have a role for that application | 0 |
38,338 | 19,103,139,352 | IssuesEvent | 2021-11-30 02:09:11 | ClickHouse/ClickHouse | https://api.github.com/repos/ClickHouse/ClickHouse | closed | slower performance when migrating to 21.2 from 20.12 | performance v21.2-affected | having some performance issue after upgrading version to 21.2(was on 20.12)
seems like select query time decreased from 10 seconds to 100 seconds:
```
version 20.12:
SELECT count()
FROM transactions_temp_3
WHERE cityHash64(casino_id, game_id, round_id, trans_id, type) NOT IN
(
SELECT row_hash
FROM transactions
ANTI RIGHT JOIN
(
SELECT cityHash64(casino_id, game_id, round_id, trans_id, type) AS row_hash
FROM transactions_temp_3
) AS x USING (row_hash)
)
SETTINGS max_threads = 16
Query id: 2e03e867-e943-4624-8d27-612b4412479e
┌─count()─┐
│ 430767 │
└─────────┘
1 rows in set. Elapsed: 10.630 sec. Processed 430.77 thousand rows, 26.19 MB (40.52 thousand rows/s., 2.46 MB/s.)
version 21.2:
SELECT count()
FROM transactions_temp_3
WHERE cityHash64(casino_id, game_id, round_id, trans_id, type) NOT IN
(
SELECT row_hash
FROM transactions
ANTI RIGHT JOIN
(
SELECT cityHash64(casino_id, game_id, round_id, trans_id, type) AS row_hash
FROM transactions_temp_3
) AS x USING (row_hash)
)
SETTINGS max_threads = 16
Query id: ef927796-2aa6-42ed-a4a0-e79de9f056a5
┌─count()─┐
│ 430767 │
└─────────┘
1 rows in set. Elapsed: 102.248 sec. Processed 430.77 thousand rows, 26.19 MB (4.21 thousand rows/s., 256.18 KB/s.)
this is the table structure:
CREATE TABLE db1.transactions
(
`event_time` DateTime,
`timestamp` DateTime,
`frb` Int8,
`is_test_account` Int8,
`country` LowCardinality(String),
`type` LowCardinality(String),
`language` LowCardinality(String),
`platform` LowCardinality(String),
`currency` LowCardinality(String),
`game_id` LowCardinality(String),
`casino_session_id` String,
`round_id` String,
`trans_id` String,
`account_id` String,
`casino_id` Int32,
`provider_id` Int32,
`amount` Decimal(18, 6),
`bonus_money` Decimal(18, 6),
`real_money` Decimal(18, 6),
`amount_eur` Decimal(18, 6),
`bonus_money_eur` Decimal(18, 6),
`real_money_eur` Decimal(18, 6),
`response_time` Int64,
`row_hash` UInt64,
INDEX idx_row_hash row_hash TYPE minmax GRANULARITY 3,
INDEX idx_round round_id TYPE bloom_filter GRANULARITY 4,
INDEX idx_trans trans_id TYPE bloom_filter GRANULARITY 100,
INDEX idx_session casino_session_id TYPE bloom_filter GRANULARITY 100,
INDEX idx_account account_id TYPE bloom_filter GRANULARITY 100,
INDEX idx_country country TYPE bloom_filter GRANULARITY 100,
INDEX idx_provider provider_id TYPE bloom_filter GRANULARITY 100
)
ENGINE = ReplicatedReplacingMergeTree('/clickhouse/sync/db1/transactions', '{replica}')
PARTITION BY toYYYYMMDD(timestamp)
ORDER BY (casino_id, game_id, round_id, trans_id, type)
TTL toDate(timestamp) + toIntervalMonth(6)
SETTINGS index_granularity = 8192
transactions_temp_3 is the same just without row_hash column, and lower ttl(1 day)
| True | slower performance when migrating to 21.2 from 20.12 - having some performance issue after upgrading version to 21.2(was on 20.12)
seems like select query time decreased from 10 seconds to 100 seconds:
```
version 20.12:
SELECT count()
FROM transactions_temp_3
WHERE cityHash64(casino_id, game_id, round_id, trans_id, type) NOT IN
(
SELECT row_hash
FROM transactions
ANTI RIGHT JOIN
(
SELECT cityHash64(casino_id, game_id, round_id, trans_id, type) AS row_hash
FROM transactions_temp_3
) AS x USING (row_hash)
)
SETTINGS max_threads = 16
Query id: 2e03e867-e943-4624-8d27-612b4412479e
┌─count()─┐
│ 430767 │
└─────────┘
1 rows in set. Elapsed: 10.630 sec. Processed 430.77 thousand rows, 26.19 MB (40.52 thousand rows/s., 2.46 MB/s.)
version 21.2:
SELECT count()
FROM transactions_temp_3
WHERE cityHash64(casino_id, game_id, round_id, trans_id, type) NOT IN
(
SELECT row_hash
FROM transactions
ANTI RIGHT JOIN
(
SELECT cityHash64(casino_id, game_id, round_id, trans_id, type) AS row_hash
FROM transactions_temp_3
) AS x USING (row_hash)
)
SETTINGS max_threads = 16
Query id: ef927796-2aa6-42ed-a4a0-e79de9f056a5
┌─count()─┐
│ 430767 │
└─────────┘
1 rows in set. Elapsed: 102.248 sec. Processed 430.77 thousand rows, 26.19 MB (4.21 thousand rows/s., 256.18 KB/s.)
this is the table structure:
CREATE TABLE db1.transactions
(
`event_time` DateTime,
`timestamp` DateTime,
`frb` Int8,
`is_test_account` Int8,
`country` LowCardinality(String),
`type` LowCardinality(String),
`language` LowCardinality(String),
`platform` LowCardinality(String),
`currency` LowCardinality(String),
`game_id` LowCardinality(String),
`casino_session_id` String,
`round_id` String,
`trans_id` String,
`account_id` String,
`casino_id` Int32,
`provider_id` Int32,
`amount` Decimal(18, 6),
`bonus_money` Decimal(18, 6),
`real_money` Decimal(18, 6),
`amount_eur` Decimal(18, 6),
`bonus_money_eur` Decimal(18, 6),
`real_money_eur` Decimal(18, 6),
`response_time` Int64,
`row_hash` UInt64,
INDEX idx_row_hash row_hash TYPE minmax GRANULARITY 3,
INDEX idx_round round_id TYPE bloom_filter GRANULARITY 4,
INDEX idx_trans trans_id TYPE bloom_filter GRANULARITY 100,
INDEX idx_session casino_session_id TYPE bloom_filter GRANULARITY 100,
INDEX idx_account account_id TYPE bloom_filter GRANULARITY 100,
INDEX idx_country country TYPE bloom_filter GRANULARITY 100,
INDEX idx_provider provider_id TYPE bloom_filter GRANULARITY 100
)
ENGINE = ReplicatedReplacingMergeTree('/clickhouse/sync/db1/transactions', '{replica}')
PARTITION BY toYYYYMMDD(timestamp)
ORDER BY (casino_id, game_id, round_id, trans_id, type)
TTL toDate(timestamp) + toIntervalMonth(6)
SETTINGS index_granularity = 8192
transactions_temp_3 is the same just without row_hash column, and lower ttl(1 day)
| non_priority | slower performance when migrating to from having some performance issue after upgrading version to was on seems like select query time decreased from seconds to seconds version select count from transactions temp where casino id game id round id trans id type not in select row hash from transactions anti right join select casino id game id round id trans id type as row hash from transactions temp as x using row hash settings max threads query id ┌─count ─┐ │ │ └─────────┘ rows in set elapsed sec processed thousand rows mb thousand rows s mb s version select count from transactions temp where casino id game id round id trans id type not in select row hash from transactions anti right join select casino id game id round id trans id type as row hash from transactions temp as x using row hash settings max threads query id ┌─count ─┐ │ │ └─────────┘ rows in set elapsed sec processed thousand rows mb thousand rows s kb s this is the table structure create table transactions event time datetime timestamp datetime frb is test account country lowcardinality string type lowcardinality string language lowcardinality string platform lowcardinality string currency lowcardinality string game id lowcardinality string casino session id string round id string trans id string account id string casino id provider id amount decimal bonus money decimal real money decimal amount eur decimal bonus money eur decimal real money eur decimal response time row hash index idx row hash row hash type minmax granularity index idx round round id type bloom filter granularity index idx trans trans id type bloom filter granularity index idx session casino session id type bloom filter granularity index idx account account id type bloom filter granularity index idx country country type bloom filter granularity index idx provider provider id type bloom filter granularity engine replicatedreplacingmergetree clickhouse sync transactions replica partition by toyyyymmdd timestamp order by casino id game id round id trans id type ttl todate timestamp tointervalmonth settings index granularity transactions temp is the same just without row hash column and lower ttl day | 0 |
274,384 | 23,835,828,993 | IssuesEvent | 2022-09-06 05:43:34 | encode/starlette | https://api.github.com/repos/encode/starlette | closed | HTTPX-based TestClient? | testclient | Hi folks,
Currently, the `TestClient` is built as a subclass of `requests.Session`.
What would be thoughts on migrating to [HTTPX](https://github.com/encode/httpx)?
- Is this a good idea at all?
- Should the `TestClient` be built *around* HTTPX, or should it eventually be *replaced* by HTTPX and its ASGI support?
As of today, there are definitely blockers to a full migration. An important one is that HTTPX doesn't support WebSocket yet (see https://github.com/encode/httpx/issues/304), while `TestClient` does.
Happy to discuss! cc @tiangolo @gvbgduh @tomchristie | 1.0 | HTTPX-based TestClient? - Hi folks,
Currently, the `TestClient` is built as a subclass of `requests.Session`.
What would be thoughts on migrating to [HTTPX](https://github.com/encode/httpx)?
- Is this a good idea at all?
- Should the `TestClient` be built *around* HTTPX, or should it eventually be *replaced* by HTTPX and its ASGI support?
As of today, there are definitely blockers to a full migration. An important one is that HTTPX doesn't support WebSocket yet (see https://github.com/encode/httpx/issues/304), while `TestClient` does.
Happy to discuss! cc @tiangolo @gvbgduh @tomchristie | non_priority | httpx based testclient hi folks currently the testclient is built as a subclass of requests session what would be thoughts on migrating to is this a good idea at all should the testclient be built around httpx or should it eventually be replaced by httpx and its asgi support as of today there are definitely blockers to a full migration an important one is that httpx doesn t support websocket yet see while testclient does happy to discuss cc tiangolo gvbgduh tomchristie | 0 |
88,635 | 10,576,301,982 | IssuesEvent | 2019-10-07 17:34:06 | sharkdp/hyperfine | https://api.github.com/repos/sharkdp/hyperfine | closed | Calculates whether the distributions of two benchmarks are different | documentation feature | Suppose we have 2 benchmarks of the same functionality in different implementations and want to know whether these distributions are differed or statistically the same.
Possible solution:
### Welch's t-test
Here is the TypeScript reference implementation that consumes the JSON output of hyperfine and calculates the probability.
```js
import * as fs from 'fs';
const sum = (x: number[]) => x.reduce((a: number, b: number) => a + b);
const sqsum = (x: number[], mu: number) =>
x.reduce((a: number, b: number) => a + (b - mu) ** 2);
const cdf = (x: number, c: number) => Math.exp(-(x ** -c));
function ttest(X: number[], Y: number[]) {
const Xn = X.length;
const Yn = Y.length;
const X_mu = sum(X) / Xn;
const Y_mu = sum(Y) / Yn;
const X_sigma = sqsum(X, X_mu) / (Xn - 1);
const Y_sigma = sqsum(Y, Y_mu) / (Yn - 1);
const t = (X_mu - Y_mu) / Math.sqrt(X_sigma / Xn + Y_sigma / Yn);
console.log(t);
return cdf(-Math.abs(t), Xn + Yn - 2) * 2.0;
}
const result = JSON.parse(fs.readFileSync('./hyperfine.json').toString());
const X = result.results[0].times;
const Y = result.results[1].times;
const p = ttest(X, Y);
console.log(p < 0.05);
``` | 1.0 | Calculates whether the distributions of two benchmarks are different - Suppose we have 2 benchmarks of the same functionality in different implementations and want to know whether these distributions are differed or statistically the same.
Possible solution:
### Welch's t-test
Here is the TypeScript reference implementation that consumes the JSON output of hyperfine and calculates the probability.
```js
import * as fs from 'fs';
const sum = (x: number[]) => x.reduce((a: number, b: number) => a + b);
const sqsum = (x: number[], mu: number) =>
x.reduce((a: number, b: number) => a + (b - mu) ** 2);
const cdf = (x: number, c: number) => Math.exp(-(x ** -c));
function ttest(X: number[], Y: number[]) {
const Xn = X.length;
const Yn = Y.length;
const X_mu = sum(X) / Xn;
const Y_mu = sum(Y) / Yn;
const X_sigma = sqsum(X, X_mu) / (Xn - 1);
const Y_sigma = sqsum(Y, Y_mu) / (Yn - 1);
const t = (X_mu - Y_mu) / Math.sqrt(X_sigma / Xn + Y_sigma / Yn);
console.log(t);
return cdf(-Math.abs(t), Xn + Yn - 2) * 2.0;
}
const result = JSON.parse(fs.readFileSync('./hyperfine.json').toString());
const X = result.results[0].times;
const Y = result.results[1].times;
const p = ttest(X, Y);
console.log(p < 0.05);
``` | non_priority | calculates whether the distributions of two benchmarks are different suppose we have benchmarks of the same functionality in different implementations and want to know whether these distributions are differed or statistically the same possible solution welch s t test here is the typescript reference implementation that consumes the json output of hyperfine and calculates the probability js import as fs from fs const sum x number x reduce a number b number a b const sqsum x number mu number x reduce a number b number a b mu const cdf x number c number math exp x c function ttest x number y number const xn x length const yn y length const x mu sum x xn const y mu sum y yn const x sigma sqsum x x mu xn const y sigma sqsum y y mu yn const t x mu y mu math sqrt x sigma xn y sigma yn console log t return cdf math abs t xn yn const result json parse fs readfilesync hyperfine json tostring const x result results times const y result results times const p ttest x y console log p | 0 |
6,990 | 3,072,588,539 | IssuesEvent | 2015-08-19 17:41:23 | Joshua-Thompson/Phenyx | https://api.github.com/repos/Joshua-Thompson/Phenyx | closed | Compile heater software requirements | documentation enhancement Heater Controller | List requirements for heater control
- how fast should it cool / heat?
- what kinds of controls are needed?
...etc | 1.0 | Compile heater software requirements - List requirements for heater control
- how fast should it cool / heat?
- what kinds of controls are needed?
...etc | non_priority | compile heater software requirements list requirements for heater control how fast should it cool heat what kinds of controls are needed etc | 0 |
205,160 | 15,594,793,500 | IssuesEvent | 2021-03-18 14:15:59 | OpenRefine/OpenRefine | https://api.github.com/repos/OpenRefine/OpenRefine | closed | Create Project from CSV test failing with "finallyCallBack is not a function" | CI/CD UI bug tests to be reviewed | The PR where this test failed is a minor backend dependency update, so I don't think it introduced the test failure.
https://github.com/OpenRefine/OpenRefine/runs/1995643484?check_suite_focus=true
```
cypress/integration/create-project/create_project.spec.js Test the create project from Web URL based on CSV:
1) cypress/integration/create-project/create_project.spec.js Test the create project from Web URL based on CSV
cypress/integration/create-project/create_project.spec.js Test the create project from Multiple Web URLs based on CSV:
✓ cypress/integration/create-project/create_project.spec.js Test the create project from Multiple Web URLs based on CSV: 6055ms
5 passing (46s)
1 failing
1) cypress/integration/create-project/create_project.spec.js
Test the create project from Web URL based on CSV:
TypeError: The following error originated from your application code, not from Cypress.
> finallyCallBack is not a function
When Cypress detects uncaught errors originating from your application it will automatically fail the current test.
This behavior is configurable, and you can choose to turn this off by listening to the `uncaught:exception` event.
https://on.cypress.io/uncaught-exception-from-application
at Object.success (http://127.0.0.1:3333/index-bundle.js:35855:13)
at fire (http://127.0.0.1:3333/index-bundle.js:3234:31)
at Object.fireWith [as resolveWith] (http://127.0.0.1:3333/index-bundle.js:3364:7)
at done (http://127.0.0.1:3333/index-bundle.js:9842:14)
at XMLHttpRequest.callback (http://127.0.0.1:3333/index-bundle.js:10313:8)
``` | 1.0 | Create Project from CSV test failing with "finallyCallBack is not a function" - The PR where this test failed is a minor backend dependency update, so I don't think it introduced the test failure.
https://github.com/OpenRefine/OpenRefine/runs/1995643484?check_suite_focus=true
```
cypress/integration/create-project/create_project.spec.js Test the create project from Web URL based on CSV:
1) cypress/integration/create-project/create_project.spec.js Test the create project from Web URL based on CSV
cypress/integration/create-project/create_project.spec.js Test the create project from Multiple Web URLs based on CSV:
✓ cypress/integration/create-project/create_project.spec.js Test the create project from Multiple Web URLs based on CSV: 6055ms
5 passing (46s)
1 failing
1) cypress/integration/create-project/create_project.spec.js
Test the create project from Web URL based on CSV:
TypeError: The following error originated from your application code, not from Cypress.
> finallyCallBack is not a function
When Cypress detects uncaught errors originating from your application it will automatically fail the current test.
This behavior is configurable, and you can choose to turn this off by listening to the `uncaught:exception` event.
https://on.cypress.io/uncaught-exception-from-application
at Object.success (http://127.0.0.1:3333/index-bundle.js:35855:13)
at fire (http://127.0.0.1:3333/index-bundle.js:3234:31)
at Object.fireWith [as resolveWith] (http://127.0.0.1:3333/index-bundle.js:3364:7)
at done (http://127.0.0.1:3333/index-bundle.js:9842:14)
at XMLHttpRequest.callback (http://127.0.0.1:3333/index-bundle.js:10313:8)
``` | non_priority | create project from csv test failing with finallycallback is not a function the pr where this test failed is a minor backend dependency update so i don t think it introduced the test failure cypress integration create project create project spec js test the create project from web url based on csv cypress integration create project create project spec js test the create project from web url based on csv cypress integration create project create project spec js test the create project from multiple web urls based on csv ✓ cypress integration create project create project spec js test the create project from multiple web urls based on csv passing failing cypress integration create project create project spec js test the create project from web url based on csv typeerror the following error originated from your application code not from cypress finallycallback is not a function when cypress detects uncaught errors originating from your application it will automatically fail the current test this behavior is configurable and you can choose to turn this off by listening to the uncaught exception event at object success at fire at object firewith at done at xmlhttprequest callback | 0 |
33,960 | 12,230,661,930 | IssuesEvent | 2020-05-04 05:39:33 | drakeg/udemy_django_vue | https://api.github.com/repos/drakeg/udemy_django_vue | opened | WS-2019-0424 (Medium) detected in elliptic-6.5.1.tgz | security vulnerability | ## WS-2019-0424 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.5.1.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.5.1.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.5.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/udemy_django_vue/final_project/frontend/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/udemy_django_vue/final_project/frontend/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- cli-plugin-babel-3.12.1.tgz (Root Library)
- webpack-4.41.2.tgz
- node-libs-browser-2.2.1.tgz
- crypto-browserify-3.12.0.tgz
- browserify-sign-4.0.4.tgz
- :x: **elliptic-6.5.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/drakeg/udemy_django_vue/commit/4266be68fe13ec8c3191715efcf06f9cc8d3bb8d">4266be68fe13ec8c3191715efcf06f9cc8d3bb8d</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
all versions before 6.5.2 of elliptic are vulnerable to Timing Attack through side-channels.
<p>Publish Date: 2019-11-13
<p>URL: <a href=https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a>WS-2019-0424</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/indutny/elliptic/pull/203/commits">https://github.com/indutny/elliptic/pull/203/commits</a></p>
<p>Release Date: 2020-04-30</p>
<p>Fix Resolution: v6.5.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0424 (Medium) detected in elliptic-6.5.1.tgz - ## WS-2019-0424 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.5.1.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.5.1.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.5.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/udemy_django_vue/final_project/frontend/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/udemy_django_vue/final_project/frontend/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- cli-plugin-babel-3.12.1.tgz (Root Library)
- webpack-4.41.2.tgz
- node-libs-browser-2.2.1.tgz
- crypto-browserify-3.12.0.tgz
- browserify-sign-4.0.4.tgz
- :x: **elliptic-6.5.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/drakeg/udemy_django_vue/commit/4266be68fe13ec8c3191715efcf06f9cc8d3bb8d">4266be68fe13ec8c3191715efcf06f9cc8d3bb8d</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
all versions before 6.5.2 of elliptic are vulnerable to Timing Attack through side-channels.
<p>Publish Date: 2019-11-13
<p>URL: <a href=https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a>WS-2019-0424</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/indutny/elliptic/pull/203/commits">https://github.com/indutny/elliptic/pull/203/commits</a></p>
<p>Release Date: 2020-04-30</p>
<p>Fix Resolution: v6.5.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in elliptic tgz ws medium severity vulnerability vulnerable library elliptic tgz ec cryptography library home page a href path to dependency file tmp ws scm udemy django vue final project frontend package json path to vulnerable library tmp ws scm udemy django vue final project frontend node modules elliptic package json dependency hierarchy cli plugin babel tgz root library webpack tgz node libs browser tgz crypto browserify tgz browserify sign tgz x elliptic tgz vulnerable library found in head commit a href vulnerability details all versions before of elliptic are vulnerable to timing attack through side channels publish date url a href cvss score details base score metrics exploitability metrics attack vector adjacent attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
18,399 | 4,266,220,183 | IssuesEvent | 2016-07-12 13:57:45 | elmsln/elmsln | https://api.github.com/repos/elmsln/elmsln | closed | Do a video showing LRS + ELMSLN + xAPI | community documentation easy ready | Rick's video from almost a year ago is the only thing we have on this. need to show what exists currently. It's getting really good. | 1.0 | Do a video showing LRS + ELMSLN + xAPI - Rick's video from almost a year ago is the only thing we have on this. need to show what exists currently. It's getting really good. | non_priority | do a video showing lrs elmsln xapi rick s video from almost a year ago is the only thing we have on this need to show what exists currently it s getting really good | 0 |
32,233 | 12,097,562,956 | IssuesEvent | 2020-04-20 08:50:31 | geea-develop/aurelia-material-sample | https://api.github.com/repos/geea-develop/aurelia-material-sample | opened | WS-2019-0017 (Medium) detected in clean-css-3.4.28.tgz | security vulnerability | ## WS-2019-0017 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>clean-css-3.4.28.tgz</b></p></summary>
<p>A well-tested CSS minifier</p>
<p>Library home page: <a href="https://registry.npmjs.org/clean-css/-/clean-css-3.4.28.tgz">https://registry.npmjs.org/clean-css/-/clean-css-3.4.28.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/aurelia-material-sample/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/aurelia-material-sample/node_modules/clean-css/package.json</p>
<p>
Dependency Hierarchy:
- aurelia-bundler-0.7.0.tgz (Root Library)
- :x: **clean-css-3.4.28.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/geea-develop/aurelia-material-sample/commit/aa98ef33dbd86011864618694ff529fb8a5e92f0">aa98ef33dbd86011864618694ff529fb8a5e92f0</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Version of clean-css prior to 4.1.11 are vulnerable to Regular Expression Denial of Service (ReDoS). Untrusted input may cause catastrophic backtracking while matching regular expressions. This can cause the application to be unresponsive leading to Denial of Service.
<p>Publish Date: 2019-02-21
<p>URL: <a href=https://github.com/jakubpawlowicz/clean-css/commit/2929bafbf8cdf7dccb24e0949c70833764fa87e3>WS-2019-0017</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/785">https://www.npmjs.com/advisories/785</a></p>
<p>Release Date: 2019-02-21</p>
<p>Fix Resolution: v4.1.11</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0017 (Medium) detected in clean-css-3.4.28.tgz - ## WS-2019-0017 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>clean-css-3.4.28.tgz</b></p></summary>
<p>A well-tested CSS minifier</p>
<p>Library home page: <a href="https://registry.npmjs.org/clean-css/-/clean-css-3.4.28.tgz">https://registry.npmjs.org/clean-css/-/clean-css-3.4.28.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/aurelia-material-sample/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/aurelia-material-sample/node_modules/clean-css/package.json</p>
<p>
Dependency Hierarchy:
- aurelia-bundler-0.7.0.tgz (Root Library)
- :x: **clean-css-3.4.28.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/geea-develop/aurelia-material-sample/commit/aa98ef33dbd86011864618694ff529fb8a5e92f0">aa98ef33dbd86011864618694ff529fb8a5e92f0</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Version of clean-css prior to 4.1.11 are vulnerable to Regular Expression Denial of Service (ReDoS). Untrusted input may cause catastrophic backtracking while matching regular expressions. This can cause the application to be unresponsive leading to Denial of Service.
<p>Publish Date: 2019-02-21
<p>URL: <a href=https://github.com/jakubpawlowicz/clean-css/commit/2929bafbf8cdf7dccb24e0949c70833764fa87e3>WS-2019-0017</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/785">https://www.npmjs.com/advisories/785</a></p>
<p>Release Date: 2019-02-21</p>
<p>Fix Resolution: v4.1.11</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in clean css tgz ws medium severity vulnerability vulnerable library clean css tgz a well tested css minifier library home page a href path to dependency file tmp ws scm aurelia material sample package json path to vulnerable library tmp ws scm aurelia material sample node modules clean css package json dependency hierarchy aurelia bundler tgz root library x clean css tgz vulnerable library found in head commit a href vulnerability details version of clean css prior to are vulnerable to regular expression denial of service redos untrusted input may cause catastrophic backtracking while matching regular expressions this can cause the application to be unresponsive leading to denial of service publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
24,277 | 12,059,247,112 | IssuesEvent | 2020-04-15 18:55:36 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | opened | CIP feature class duplicates delition | Service: Geo Type: Map Request Workgroup: CPO | The Corridor Program office has identified projects in the CIP feature class in Datamart that have ATD_ADMIN duplicates. We need to delete the ATD_ADMIN duplicates so that only the CPO projects are retained in the CIP feature class in Datamart. | 1.0 | CIP feature class duplicates delition - The Corridor Program office has identified projects in the CIP feature class in Datamart that have ATD_ADMIN duplicates. We need to delete the ATD_ADMIN duplicates so that only the CPO projects are retained in the CIP feature class in Datamart. | non_priority | cip feature class duplicates delition the corridor program office has identified projects in the cip feature class in datamart that have atd admin duplicates we need to delete the atd admin duplicates so that only the cpo projects are retained in the cip feature class in datamart | 0 |
112,647 | 17,095,342,730 | IssuesEvent | 2021-07-09 01:03:45 | samq-wsdemo/cargo-audit | https://api.github.com/repos/samq-wsdemo/cargo-audit | opened | CVE-2021-32714 (Medium) detected in hyper-0.13.10.crate | security vulnerability | ## CVE-2021-32714 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>hyper-0.13.10.crate</b></p></summary>
<p>A fast and correct HTTP library.</p>
<p>Library home page: <a href="https://crates.io/api/v1/crates/hyper/0.13.10/download">https://crates.io/api/v1/crates/hyper/0.13.10/download</a></p>
<p>
Dependency Hierarchy:
- rustsec-0.23.3.crate (Root Library)
- cargo-edit-0.7.0.crate
- reqwest-0.10.10.crate
- :x: **hyper-0.13.10.crate** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
hyper is an HTTP library for Rust. In versions prior to 0.14.10, hyper's HTTP server and client code had a flaw that could trigger an integer overflow when decoding chunk sizes that are too big. This allows possible data loss, or if combined with an upstream HTTP proxy that allows chunk sizes larger than hyper does, can result in "request smuggling" or "desync attacks." The vulnerability is patched in version 0.14.10. Two possible workarounds exist. One may reject requests manually that contain a `Transfer-Encoding` header or ensure any upstream proxy rejects `Transfer-Encoding` chunk sizes greater than what fits in 64-bit unsigned integers.
<p>Publish Date: 2021-07-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32714>CVE-2021-32714</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-32714">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-32714</a></p>
<p>Release Date: 2021-07-07</p>
<p>Fix Resolution: hyper - 0.14.10</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Crate","packageName":"hyper","packageVersion":"0.13.10","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"rustsec:0.23.3;cargo-edit:0.7.0;reqwest:0.10.10;hyper:0.13.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"hyper - 0.14.10"}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-32714","vulnerabilityDetails":"hyper is an HTTP library for Rust. In versions prior to 0.14.10, hyper\u0027s HTTP server and client code had a flaw that could trigger an integer overflow when decoding chunk sizes that are too big. This allows possible data loss, or if combined with an upstream HTTP proxy that allows chunk sizes larger than hyper does, can result in \"request smuggling\" or \"desync attacks.\" The vulnerability is patched in version 0.14.10. Two possible workarounds exist. One may reject requests manually that contain a `Transfer-Encoding` header or ensure any upstream proxy rejects `Transfer-Encoding` chunk sizes greater than what fits in 64-bit unsigned integers.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32714","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-32714 (Medium) detected in hyper-0.13.10.crate - ## CVE-2021-32714 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>hyper-0.13.10.crate</b></p></summary>
<p>A fast and correct HTTP library.</p>
<p>Library home page: <a href="https://crates.io/api/v1/crates/hyper/0.13.10/download">https://crates.io/api/v1/crates/hyper/0.13.10/download</a></p>
<p>
Dependency Hierarchy:
- rustsec-0.23.3.crate (Root Library)
- cargo-edit-0.7.0.crate
- reqwest-0.10.10.crate
- :x: **hyper-0.13.10.crate** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
hyper is an HTTP library for Rust. In versions prior to 0.14.10, hyper's HTTP server and client code had a flaw that could trigger an integer overflow when decoding chunk sizes that are too big. This allows possible data loss, or if combined with an upstream HTTP proxy that allows chunk sizes larger than hyper does, can result in "request smuggling" or "desync attacks." The vulnerability is patched in version 0.14.10. Two possible workarounds exist. One may reject requests manually that contain a `Transfer-Encoding` header or ensure any upstream proxy rejects `Transfer-Encoding` chunk sizes greater than what fits in 64-bit unsigned integers.
<p>Publish Date: 2021-07-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32714>CVE-2021-32714</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-32714">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-32714</a></p>
<p>Release Date: 2021-07-07</p>
<p>Fix Resolution: hyper - 0.14.10</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Crate","packageName":"hyper","packageVersion":"0.13.10","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"rustsec:0.23.3;cargo-edit:0.7.0;reqwest:0.10.10;hyper:0.13.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"hyper - 0.14.10"}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-32714","vulnerabilityDetails":"hyper is an HTTP library for Rust. In versions prior to 0.14.10, hyper\u0027s HTTP server and client code had a flaw that could trigger an integer overflow when decoding chunk sizes that are too big. This allows possible data loss, or if combined with an upstream HTTP proxy that allows chunk sizes larger than hyper does, can result in \"request smuggling\" or \"desync attacks.\" The vulnerability is patched in version 0.14.10. Two possible workarounds exist. One may reject requests manually that contain a `Transfer-Encoding` header or ensure any upstream proxy rejects `Transfer-Encoding` chunk sizes greater than what fits in 64-bit unsigned integers.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32714","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in hyper crate cve medium severity vulnerability vulnerable library hyper crate a fast and correct http library library home page a href dependency hierarchy rustsec crate root library cargo edit crate reqwest crate x hyper crate vulnerable library found in base branch main vulnerability details hyper is an http library for rust in versions prior to hyper s http server and client code had a flaw that could trigger an integer overflow when decoding chunk sizes that are too big this allows possible data loss or if combined with an upstream http proxy that allows chunk sizes larger than hyper does can result in request smuggling or desync attacks the vulnerability is patched in version two possible workarounds exist one may reject requests manually that contain a transfer encoding header or ensure any upstream proxy rejects transfer encoding chunk sizes greater than what fits in bit unsigned integers publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution hyper isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree rustsec cargo edit reqwest hyper isminimumfixversionavailable true minimumfixversion hyper basebranches vulnerabilityidentifier cve vulnerabilitydetails hyper is an http library for rust in versions prior to hyper http server and client code had a flaw that could trigger an integer overflow when decoding chunk sizes that are too big this allows possible data loss or if combined with an upstream http proxy that allows chunk sizes larger than hyper does can result in request smuggling or desync attacks the vulnerability is patched in version two possible workarounds exist one may reject requests manually that contain a transfer encoding header or ensure any upstream proxy rejects transfer encoding chunk sizes greater than what fits in bit unsigned integers vulnerabilityurl | 0 |
168,011 | 26,581,143,242 | IssuesEvent | 2023-01-22 13:21:12 | psf/black | https://api.github.com/repos/psf/black | closed | Format the hex codes in Unicode/hex escape sequences (`\U`, `\u`, `\x`) in string literals | T: design F: strings | **Is your feature request related to a problem? Please describe.**
Currently, one can write either `"\U0001f977"` or `"\U0001F977"` which are equivalent but they look differently. Similarly, one can write `"\u200b"` or `"\u200B"` which also are equivalent but they look differently (do mind that `\U` and `\u` are NOT equivalent though; unless we also want to talk about shortening `"\U0000200b"` to `"\u200b"` which I guess would make sense but is probably a separate issue).
Right now, I'm forced to think whether I should use uppercase or lowercase letters as Black doesn't enforce it.
**Describe the solution you'd like**
I think it would make sense to have these be consistent in some way, possibly in the same way as the numeric literals, although personally, I think it would make more sense to have it all uppercase in case of `\U0001F977` and all lowercase in case of `\u200b`. I definitely think that the `\u200b` should not be `\u200B` but I don't have a strong opinion on the `\U0001f977` vs `\U0001F977`.
**Describe alternatives you've considered**
Alternatives were not considered.
**Additional context**
None.
| 1.0 | Format the hex codes in Unicode/hex escape sequences (`\U`, `\u`, `\x`) in string literals - **Is your feature request related to a problem? Please describe.**
Currently, one can write either `"\U0001f977"` or `"\U0001F977"` which are equivalent but they look differently. Similarly, one can write `"\u200b"` or `"\u200B"` which also are equivalent but they look differently (do mind that `\U` and `\u` are NOT equivalent though; unless we also want to talk about shortening `"\U0000200b"` to `"\u200b"` which I guess would make sense but is probably a separate issue).
Right now, I'm forced to think whether I should use uppercase or lowercase letters as Black doesn't enforce it.
**Describe the solution you'd like**
I think it would make sense to have these be consistent in some way, possibly in the same way as the numeric literals, although personally, I think it would make more sense to have it all uppercase in case of `\U0001F977` and all lowercase in case of `\u200b`. I definitely think that the `\u200b` should not be `\u200B` but I don't have a strong opinion on the `\U0001f977` vs `\U0001F977`.
**Describe alternatives you've considered**
Alternatives were not considered.
**Additional context**
None.
| non_priority | format the hex codes in unicode hex escape sequences u u x in string literals is your feature request related to a problem please describe currently one can write either or which are equivalent but they look differently similarly one can write or which also are equivalent but they look differently do mind that u and u are not equivalent though unless we also want to talk about shortening to which i guess would make sense but is probably a separate issue right now i m forced to think whether i should use uppercase or lowercase letters as black doesn t enforce it describe the solution you d like i think it would make sense to have these be consistent in some way possibly in the same way as the numeric literals although personally i think it would make more sense to have it all uppercase in case of and all lowercase in case of i definitely think that the should not be but i don t have a strong opinion on the vs describe alternatives you ve considered alternatives were not considered additional context none | 0 |
45,668 | 24,160,871,567 | IssuesEvent | 2022-09-22 11:32:14 | zio/zio | https://api.github.com/repos/zio/zio | closed | Performance regression in 2.0.0+ | stream performance | I recently bumped the ZIO version in my application from 1.0.15 to 2.0.0 and noticed a significant performance regression in part of the workload, which involves substantial use of `ZStream` to read data from (very large) archive files, decode it from UTF-8, perform some other transformations in memory, and then write the data to disk again.
Although I haven't isolated the issue yet, the ZIO overhead appears to be much higher than it had been before the update. The screenshot below from the jprofiler hotspot view was captured as the application ran the workload in question. (This screenshot is actually from the application running against ZIO 2.0.2, which I tried after first observing the performance regression when running with ZIO 2.0.0.)
<img width="787" alt="image" src="https://user-images.githubusercontent.com/375423/189431290-4614bbd4-db8f-43bf-bdad-6e86e125f928.png">
| True | Performance regression in 2.0.0+ - I recently bumped the ZIO version in my application from 1.0.15 to 2.0.0 and noticed a significant performance regression in part of the workload, which involves substantial use of `ZStream` to read data from (very large) archive files, decode it from UTF-8, perform some other transformations in memory, and then write the data to disk again.
Although I haven't isolated the issue yet, the ZIO overhead appears to be much higher than it had been before the update. The screenshot below from the jprofiler hotspot view was captured as the application ran the workload in question. (This screenshot is actually from the application running against ZIO 2.0.2, which I tried after first observing the performance regression when running with ZIO 2.0.0.)
<img width="787" alt="image" src="https://user-images.githubusercontent.com/375423/189431290-4614bbd4-db8f-43bf-bdad-6e86e125f928.png">
| non_priority | performance regression in i recently bumped the zio version in my application from to and noticed a significant performance regression in part of the workload which involves substantial use of zstream to read data from very large archive files decode it from utf perform some other transformations in memory and then write the data to disk again although i haven t isolated the issue yet the zio overhead appears to be much higher than it had been before the update the screenshot below from the jprofiler hotspot view was captured as the application ran the workload in question this screenshot is actually from the application running against zio which i tried after first observing the performance regression when running with zio img width alt image src | 0 |
56,684 | 15,288,299,149 | IssuesEvent | 2021-02-23 16:42:51 | department-of-veterans-affairs/va.gov-cms | https://api.github.com/repos/department-of-veterans-affairs/va.gov-cms | closed | composer va:web:build fails on Jenkins/BRD only and not on PR or local environments | Defect DevOps Drupal engineering Stretch goal | ## Problem statement
Issues with `vets-website` package break the build on BRD only and not on local or PR environments.
This causes unexpected delays in CMS deployment schedule.
Build breaking events like these should be caught in Tugboat / local environments, so that the team can react sooner.
Broken build sample: http://jenkins.vfs.va.gov/job/testing/job/cms-post-deploy-tests-staging/229/consoleFull
`Error: Cannot find module 'chokidar'`
## Acceptance Criteria
- [ ] `composer va:web:build` fails / behaves in the same manner on all types of environments: BRD, Tugboat, local.
| 1.0 | composer va:web:build fails on Jenkins/BRD only and not on PR or local environments - ## Problem statement
Issues with `vets-website` package break the build on BRD only and not on local or PR environments.
This causes unexpected delays in CMS deployment schedule.
Build breaking events like these should be caught in Tugboat / local environments, so that the team can react sooner.
Broken build sample: http://jenkins.vfs.va.gov/job/testing/job/cms-post-deploy-tests-staging/229/consoleFull
`Error: Cannot find module 'chokidar'`
## Acceptance Criteria
- [ ] `composer va:web:build` fails / behaves in the same manner on all types of environments: BRD, Tugboat, local.
| non_priority | composer va web build fails on jenkins brd only and not on pr or local environments problem statement issues with vets website package break the build on brd only and not on local or pr environments this causes unexpected delays in cms deployment schedule build breaking events like these should be caught in tugboat local environments so that the team can react sooner broken build sample error cannot find module chokidar acceptance criteria composer va web build fails behaves in the same manner on all types of environments brd tugboat local | 0 |
31,479 | 14,974,913,916 | IssuesEvent | 2021-01-28 04:49:49 | ermiry/cerver-client | https://api.github.com/repos/ermiry/cerver-client | closed | Refactor connection_update () to only use one packet buffer | client connection performance | Currently connection_update () has a loop in which each cycle a call to client_receive () is performed in which every time, a new packet buffer buffer is allocated and then deleted after the packets have been handled. This can be avoided, to increase performance, by only allocating a packet buffer once in connection_update () and using it through the duration of the connection. | True | Refactor connection_update () to only use one packet buffer - Currently connection_update () has a loop in which each cycle a call to client_receive () is performed in which every time, a new packet buffer buffer is allocated and then deleted after the packets have been handled. This can be avoided, to increase performance, by only allocating a packet buffer once in connection_update () and using it through the duration of the connection. | non_priority | refactor connection update to only use one packet buffer currently connection update has a loop in which each cycle a call to client receive is performed in which every time a new packet buffer buffer is allocated and then deleted after the packets have been handled this can be avoided to increase performance by only allocating a packet buffer once in connection update and using it through the duration of the connection | 0 |
170,405 | 26,955,113,164 | IssuesEvent | 2023-02-08 14:25:31 | Regalis11/Barotrauma | https://api.github.com/repos/Regalis11/Barotrauma | closed | [SUBMARINE] [TYPHON 1] Various issues with walls, sprite layers and hulls | Bug Design | - [x] I have searched the issue tracker to check if the issue has already been reported.
**Description**
First Typhon has a lot of issues starting with internal hull-less area, unnecessary double walls and serious sprite depth issues.
1. Hull
There is hull-less area between electrical and closest to the airlock access shaft. This area can lead to flooding without external damage to submarine (due to accident's or griefing)
**Possible solution**
Extend the electrical room to top and right

2. Double walls
a. Double walls can be a problem for monster's AI. This also create issue in the armory when if top wall is breached armory will flood but there won't be visual indication of that because second wall is intact.

b. Wall between medbay and crew quarters has this issue and issue (https://github.com/Regalis11/Barotrauma/issues/4873) with possible undrainability.
c. Bottom walls can be removed and replaced with backwalls or other purely decorative supports.
**Possible solutions**
a. Double wall between gunneries can be replaced with a single wall (without cables) with size of 1.150 and Y texture scale of 0.5. Some hull rearrangement is also advised
b. Wall between medbay and crew quarters can be made like this and decorative wires and/or pipes can be added if necessary
c. Bottom walls can be removed and replaced with backwalls or other purely decorative supports.
3. Sprite layering issues
a. Central Access Passage, right side has serious sprite layering issues regarding props and background walls, they have identical depth values which make them look like this

b. Central Access Passage, right side also has some strange looking prop placement, particular vents, columns, supply cabinet and loose panel.
**Possible solution**
a. Set props like cabinets, columns, etc. to have sprite depth values lover than background wall
b. Rearrange decoration placements or even replace "Outpost Airlock Wall" background with something else, possibly some solid background


**Steps To Reproduce**
Inspect Typhon in subeditor or in game. Layering issue may look different for different users.
**Version**
Stable, 0.15.1.0 | 1.0 | [SUBMARINE] [TYPHON 1] Various issues with walls, sprite layers and hulls - - [x] I have searched the issue tracker to check if the issue has already been reported.
**Description**
First Typhon has a lot of issues starting with internal hull-less area, unnecessary double walls and serious sprite depth issues.
1. Hull
There is hull-less area between electrical and closest to the airlock access shaft. This area can lead to flooding without external damage to submarine (due to accident's or griefing)
**Possible solution**
Extend the electrical room to top and right

2. Double walls
a. Double walls can be a problem for monster's AI. This also create issue in the armory when if top wall is breached armory will flood but there won't be visual indication of that because second wall is intact.

b. Wall between medbay and crew quarters has this issue and issue (https://github.com/Regalis11/Barotrauma/issues/4873) with possible undrainability.
c. Bottom walls can be removed and replaced with backwalls or other purely decorative supports.
**Possible solutions**
a. Double wall between gunneries can be replaced with a single wall (without cables) with size of 1.150 and Y texture scale of 0.5. Some hull rearrangement is also advised
b. Wall between medbay and crew quarters can be made like this and decorative wires and/or pipes can be added if necessary
c. Bottom walls can be removed and replaced with backwalls or other purely decorative supports.
3. Sprite layering issues
a. Central Access Passage, right side has serious sprite layering issues regarding props and background walls, they have identical depth values which make them look like this

b. Central Access Passage, right side also has some strange looking prop placement, particular vents, columns, supply cabinet and loose panel.
**Possible solution**
a. Set props like cabinets, columns, etc. to have sprite depth values lover than background wall
b. Rearrange decoration placements or even replace "Outpost Airlock Wall" background with something else, possibly some solid background


**Steps To Reproduce**
Inspect Typhon in subeditor or in game. Layering issue may look different for different users.
**Version**
Stable, 0.15.1.0 | non_priority | various issues with walls sprite layers and hulls i have searched the issue tracker to check if the issue has already been reported description first typhon has a lot of issues starting with internal hull less area unnecessary double walls and serious sprite depth issues hull there is hull less area between electrical and closest to the airlock access shaft this area can lead to flooding without external damage to submarine due to accident s or griefing possible solution extend the electrical room to top and right double walls a double walls can be a problem for monster s ai this also create issue in the armory when if top wall is breached armory will flood but there won t be visual indication of that because second wall is intact b wall between medbay and crew quarters has this issue and issue with possible undrainability c bottom walls can be removed and replaced with backwalls or other purely decorative supports possible solutions a double wall between gunneries can be replaced with a single wall without cables with size of and y texture scale of some hull rearrangement is also advised b wall between medbay and crew quarters can be made like this and decorative wires and or pipes can be added if necessary c bottom walls can be removed and replaced with backwalls or other purely decorative supports sprite layering issues a central access passage right side has serious sprite layering issues regarding props and background walls they have identical depth values which make them look like this b central access passage right side also has some strange looking prop placement particular vents columns supply cabinet and loose panel possible solution a set props like cabinets columns etc to have sprite depth values lover than background wall b rearrange decoration placements or even replace outpost airlock wall background with something else possibly some solid background steps to reproduce inspect typhon in subeditor or in game layering issue may look different for different users version stable | 0 |
114,822 | 9,761,724,396 | IssuesEvent | 2019-06-05 09:28:06 | scala-native/scala-native | https://api.github.com/repos/scala-native/scala-native | closed | Tests fail with exception message that is not helpful | bug component:tests | The cause of this error is triggered by a change to the upper/lower case encoding as far as I can tell. This is confirmed locally and on Travis CI which was run to confirm the failure. There is definitely some issues I found in the encoding in this PR https://github.com/scala-native/scala-native/pull/1611 but I don't think that this would cause what seems to be an exception in the test harness code. I believe the error message could be improved and factored out or the exception code factored out to become DRY. Here is the place the exception is throw in the code.
https://github.com/scala-native/scala-native/blob/34453c01ba344b3fe3bf4a79ec4b10bf07638e72/unit-tests/src/test/scala/scala/scalanative/regex/GoTestUtils.scala#L25
The following is the error stack trace and the run context. The message at the end is a big improvement over the previous test harness messages. Thanks @LeeTibbert
```
> tests/testOnly java.lang.CharacterSuite*
...
[info] Compiling 1 Scala source to /Users/eric/workspace/scala-native/unit-tests/target/scala-2.11/test-classes...
[info] Linking (3674 ms)
[info] Checking intermediate code (1314 ms)
[info] Dumping intermediate code (1742 ms)
[info] Discovered 5751 classes and 31508 methods
[info] Optimizing (debug mode) (10637 ms)
[info] Checking intermediate code (614 ms)
[info] Dumping intermediate code (1190 ms)
[info] Generating intermediate code (12387 ms)
[info] Produced 8 files
[info] Compiling to native code (6602 ms)
[info] Linking native code (immix gc, none lto) (636 ms)
[info] Total (39339 ms)
[info] Starting process '/Users/eric/workspace/scala-native/unit-tests/target/scala-2.11/tests-out' on port '61847'.
[error] java.lang.IllegalStateException: can't happen
[error] at java.lang.Throwable.fillInStackTrace(Unknown Source)
[error] at java.lang.IllegalStateException.<init>(Unknown Source)
[error] at scala.scalanative.regex.RE2$.compileImpl(Unknown Source)
[error] at scala.scalanative.regex.Pattern$.compile(Unknown Source)
[error] at scala.scalanative.regex.Pattern$.compile(Unknown Source)
[error] at java.util.regex.Pattern$.compile(Unknown Source)
[error] at java.util.regex.Pattern$.compile(Unknown Source)
[error] at scala.collection.immutable.StringLike$class.r(Unknown Source)
[error] at scala.collection.immutable.StringOps.r(Unknown Source)
[error] at scala.collection.immutable.StringLike$class.r(Unknown Source)
[error] at scala.collection.immutable.StringOps.r(Unknown Source)
[error] at java.nio.file.FilesSuite$.<init>(Unknown Source)
[error] at <none>._SM25java.nio.file.FilesSuite$G4load(Unknown Source)
[error] at scala.scalanative.testinterface.TestMain$.<init>(Unknown Source)
[error] at <none>._SM41scala.scalanative.testinterface.TestMain$G4load(Unknown Source)
[error] at <none>.main(Unknown Source)
[trace] Stack trace suppressed: run last tests/nativetest:testOnly for the full output.
[error] (tests/nativetest:testOnly) scala.scalanative.build.BuildException: The test program never connected to the test runner.
``` | 1.0 | Tests fail with exception message that is not helpful - The cause of this error is triggered by a change to the upper/lower case encoding as far as I can tell. This is confirmed locally and on Travis CI which was run to confirm the failure. There is definitely some issues I found in the encoding in this PR https://github.com/scala-native/scala-native/pull/1611 but I don't think that this would cause what seems to be an exception in the test harness code. I believe the error message could be improved and factored out or the exception code factored out to become DRY. Here is the place the exception is throw in the code.
https://github.com/scala-native/scala-native/blob/34453c01ba344b3fe3bf4a79ec4b10bf07638e72/unit-tests/src/test/scala/scala/scalanative/regex/GoTestUtils.scala#L25
The following is the error stack trace and the run context. The message at the end is a big improvement over the previous test harness messages. Thanks @LeeTibbert
```
> tests/testOnly java.lang.CharacterSuite*
...
[info] Compiling 1 Scala source to /Users/eric/workspace/scala-native/unit-tests/target/scala-2.11/test-classes...
[info] Linking (3674 ms)
[info] Checking intermediate code (1314 ms)
[info] Dumping intermediate code (1742 ms)
[info] Discovered 5751 classes and 31508 methods
[info] Optimizing (debug mode) (10637 ms)
[info] Checking intermediate code (614 ms)
[info] Dumping intermediate code (1190 ms)
[info] Generating intermediate code (12387 ms)
[info] Produced 8 files
[info] Compiling to native code (6602 ms)
[info] Linking native code (immix gc, none lto) (636 ms)
[info] Total (39339 ms)
[info] Starting process '/Users/eric/workspace/scala-native/unit-tests/target/scala-2.11/tests-out' on port '61847'.
[error] java.lang.IllegalStateException: can't happen
[error] at java.lang.Throwable.fillInStackTrace(Unknown Source)
[error] at java.lang.IllegalStateException.<init>(Unknown Source)
[error] at scala.scalanative.regex.RE2$.compileImpl(Unknown Source)
[error] at scala.scalanative.regex.Pattern$.compile(Unknown Source)
[error] at scala.scalanative.regex.Pattern$.compile(Unknown Source)
[error] at java.util.regex.Pattern$.compile(Unknown Source)
[error] at java.util.regex.Pattern$.compile(Unknown Source)
[error] at scala.collection.immutable.StringLike$class.r(Unknown Source)
[error] at scala.collection.immutable.StringOps.r(Unknown Source)
[error] at scala.collection.immutable.StringLike$class.r(Unknown Source)
[error] at scala.collection.immutable.StringOps.r(Unknown Source)
[error] at java.nio.file.FilesSuite$.<init>(Unknown Source)
[error] at <none>._SM25java.nio.file.FilesSuite$G4load(Unknown Source)
[error] at scala.scalanative.testinterface.TestMain$.<init>(Unknown Source)
[error] at <none>._SM41scala.scalanative.testinterface.TestMain$G4load(Unknown Source)
[error] at <none>.main(Unknown Source)
[trace] Stack trace suppressed: run last tests/nativetest:testOnly for the full output.
[error] (tests/nativetest:testOnly) scala.scalanative.build.BuildException: The test program never connected to the test runner.
``` | non_priority | tests fail with exception message that is not helpful the cause of this error is triggered by a change to the upper lower case encoding as far as i can tell this is confirmed locally and on travis ci which was run to confirm the failure there is definitely some issues i found in the encoding in this pr but i don t think that this would cause what seems to be an exception in the test harness code i believe the error message could be improved and factored out or the exception code factored out to become dry here is the place the exception is throw in the code the following is the error stack trace and the run context the message at the end is a big improvement over the previous test harness messages thanks leetibbert tests testonly java lang charactersuite compiling scala source to users eric workspace scala native unit tests target scala test classes linking ms checking intermediate code ms dumping intermediate code ms discovered classes and methods optimizing debug mode ms checking intermediate code ms dumping intermediate code ms generating intermediate code ms produced files compiling to native code ms linking native code immix gc none lto ms total ms starting process users eric workspace scala native unit tests target scala tests out on port java lang illegalstateexception can t happen at java lang throwable fillinstacktrace unknown source at java lang illegalstateexception unknown source at scala scalanative regex compileimpl unknown source at scala scalanative regex pattern compile unknown source at scala scalanative regex pattern compile unknown source at java util regex pattern compile unknown source at java util regex pattern compile unknown source at scala collection immutable stringlike class r unknown source at scala collection immutable stringops r unknown source at scala collection immutable stringlike class r unknown source at scala collection immutable stringops r unknown source at java nio file filessuite unknown source at nio file filessuite unknown source at scala scalanative testinterface testmain unknown source at scalanative testinterface testmain unknown source at main unknown source stack trace suppressed run last tests nativetest testonly for the full output tests nativetest testonly scala scalanative build buildexception the test program never connected to the test runner | 0 |
289,684 | 25,004,431,945 | IssuesEvent | 2022-11-03 10:39:49 | kubermatic/dashboard | https://api.github.com/repos/kubermatic/dashboard | opened | UI-Testing - Release 2.22 | testing | This will contain UI testing tickets for features in KKP 2.22 Releases | 1.0 | UI-Testing - Release 2.22 - This will contain UI testing tickets for features in KKP 2.22 Releases | non_priority | ui testing release this will contain ui testing tickets for features in kkp releases | 0 |
141,906 | 12,991,784,810 | IssuesEvent | 2020-07-23 04:54:05 | CSharpGroup3/ClassicYogaAshram | https://api.github.com/repos/CSharpGroup3/ClassicYogaAshram | closed | Создание Wiki инструкции для команды по работе с ветками | documentation | ### Создание Wiki инструкции по работе с ветками
**Конечный результат:**
Добавить инструкцию для разработчиков по работе с ветками
**План решения:**
Написать разъяснение об основных ветках и правил именовании новых веток.
**Мотивация:**
Предотвратить возникновения недопонимании среди разработчиков и ошибок при слиянии веток.
**Критерии приёмки:**
Планируемое время работы:
30 минут | 1.0 | Создание Wiki инструкции для команды по работе с ветками - ### Создание Wiki инструкции по работе с ветками
**Конечный результат:**
Добавить инструкцию для разработчиков по работе с ветками
**План решения:**
Написать разъяснение об основных ветках и правил именовании новых веток.
**Мотивация:**
Предотвратить возникновения недопонимании среди разработчиков и ошибок при слиянии веток.
**Критерии приёмки:**
Планируемое время работы:
30 минут | non_priority | создание wiki инструкции для команды по работе с ветками создание wiki инструкции по работе с ветками конечный результат добавить инструкцию для разработчиков по работе с ветками план решения написать разъяснение об основных ветках и правил именовании новых веток мотивация предотвратить возникновения недопонимании среди разработчиков и ошибок при слиянии веток критерии приёмки планируемое время работы минут | 0 |
119,671 | 15,595,933,439 | IssuesEvent | 2021-03-18 15:21:57 | LITO-apps/Treevel-client | https://api.github.com/repos/LITO-apps/Treevel-client | closed | AimingMeteoriteGimmickのデザイン草案作成 | 4 design ゲーム画面 | ### 終了条件
- 草案資料を作成する
##### Meteoriteと同じ
- モチーフ
#### Meteoriteとの違い
特定のBottleを狙ったことを知らせる必要ある
- 影の部分の登場方法
- 色
- 軌跡(?)
- Game開始時に、狙われているBottleを知らせる | 1.0 | AimingMeteoriteGimmickのデザイン草案作成 - ### 終了条件
- 草案資料を作成する
##### Meteoriteと同じ
- モチーフ
#### Meteoriteとの違い
特定のBottleを狙ったことを知らせる必要ある
- 影の部分の登場方法
- 色
- 軌跡(?)
- Game開始時に、狙われているBottleを知らせる | non_priority | aimingmeteoritegimmickのデザイン草案作成 終了条件 草案資料を作成する meteoriteと同じ モチーフ meteoriteとの違い 特定のbottleを狙ったことを知らせる必要ある 影の部分の登場方法 色 軌跡 game開始時に、狙われているbottleを知らせる | 0 |
55,187 | 13,994,639,901 | IssuesEvent | 2020-10-28 01:13:55 | LevyForchh/gvisor | https://api.github.com/repos/LevyForchh/gvisor | opened | CVE-2020-14422 (Medium) detected in ipaddress-1.0.23-py2.py3-none-any.whl | security vulnerability | ## CVE-2020-14422 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ipaddress-1.0.23-py2.py3-none-any.whl</b></p></summary>
<p>IPv4/IPv6 manipulation library</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/c2/f8/49697181b1651d8347d24c095ce46c7346c37335ddc7d255833e7cde674d/ipaddress-1.0.23-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/c2/f8/49697181b1651d8347d24c095ce46c7346c37335ddc7d255833e7cde674d/ipaddress-1.0.23-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: gvisor/benchmarks/requirements.txt</p>
<p>Path to vulnerable library: gvisor/benchmarks/requirements.txt</p>
<p>
Dependency Hierarchy:
- docker-3.7.0-py2.py3-none-any.whl (Root Library)
- :x: **ipaddress-1.0.23-py2.py3-none-any.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Lib/ipaddress.py in Python through 3.8.3 improperly computes hash values in the IPv4Interface and IPv6Interface classes, which might allow a remote attacker to cause a denial of service if an application is affected by the performance of a dictionary containing IPv4Interface or IPv6Interface objects, and this attacker can cause many dictionary entries to be created.
<p>Publish Date: 2020-06-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14422>CVE-2020-14422</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://security-tracker.debian.org/tracker/CVE-2020-14422">https://security-tracker.debian.org/tracker/CVE-2020-14422</a></p>
<p>Release Date: 2020-06-18</p>
<p>Fix Resolution: 3.5.3-1+deb9u2, 3.7.3-2+deb10u2, 3.8.4~rc1-1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"ipaddress","packageVersion":"1.0.23","isTransitiveDependency":true,"dependencyTree":"docker:3.7.0;ipaddress:1.0.23","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.5.3-1+deb9u2, 3.7.3-2+deb10u2, 3.8.4~rc1-1"}],"vulnerabilityIdentifier":"CVE-2020-14422","vulnerabilityDetails":"Lib/ipaddress.py in Python through 3.8.3 improperly computes hash values in the IPv4Interface and IPv6Interface classes, which might allow a remote attacker to cause a denial of service if an application is affected by the performance of a dictionary containing IPv4Interface or IPv6Interface objects, and this attacker can cause many dictionary entries to be created.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14422","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-14422 (Medium) detected in ipaddress-1.0.23-py2.py3-none-any.whl - ## CVE-2020-14422 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ipaddress-1.0.23-py2.py3-none-any.whl</b></p></summary>
<p>IPv4/IPv6 manipulation library</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/c2/f8/49697181b1651d8347d24c095ce46c7346c37335ddc7d255833e7cde674d/ipaddress-1.0.23-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/c2/f8/49697181b1651d8347d24c095ce46c7346c37335ddc7d255833e7cde674d/ipaddress-1.0.23-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: gvisor/benchmarks/requirements.txt</p>
<p>Path to vulnerable library: gvisor/benchmarks/requirements.txt</p>
<p>
Dependency Hierarchy:
- docker-3.7.0-py2.py3-none-any.whl (Root Library)
- :x: **ipaddress-1.0.23-py2.py3-none-any.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Lib/ipaddress.py in Python through 3.8.3 improperly computes hash values in the IPv4Interface and IPv6Interface classes, which might allow a remote attacker to cause a denial of service if an application is affected by the performance of a dictionary containing IPv4Interface or IPv6Interface objects, and this attacker can cause many dictionary entries to be created.
<p>Publish Date: 2020-06-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14422>CVE-2020-14422</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://security-tracker.debian.org/tracker/CVE-2020-14422">https://security-tracker.debian.org/tracker/CVE-2020-14422</a></p>
<p>Release Date: 2020-06-18</p>
<p>Fix Resolution: 3.5.3-1+deb9u2, 3.7.3-2+deb10u2, 3.8.4~rc1-1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"ipaddress","packageVersion":"1.0.23","isTransitiveDependency":true,"dependencyTree":"docker:3.7.0;ipaddress:1.0.23","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.5.3-1+deb9u2, 3.7.3-2+deb10u2, 3.8.4~rc1-1"}],"vulnerabilityIdentifier":"CVE-2020-14422","vulnerabilityDetails":"Lib/ipaddress.py in Python through 3.8.3 improperly computes hash values in the IPv4Interface and IPv6Interface classes, which might allow a remote attacker to cause a denial of service if an application is affected by the performance of a dictionary containing IPv4Interface or IPv6Interface objects, and this attacker can cause many dictionary entries to be created.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14422","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in ipaddress none any whl cve medium severity vulnerability vulnerable library ipaddress none any whl manipulation library library home page a href path to dependency file gvisor benchmarks requirements txt path to vulnerable library gvisor benchmarks requirements txt dependency hierarchy docker none any whl root library x ipaddress none any whl vulnerable library vulnerability details lib ipaddress py in python through improperly computes hash values in the and classes which might allow a remote attacker to cause a denial of service if an application is affected by the performance of a dictionary containing or objects and this attacker can cause many dictionary entries to be created publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails lib ipaddress py in python through improperly computes hash values in the and classes which might allow a remote attacker to cause a denial of service if an application is affected by the performance of a dictionary containing or objects and this attacker can cause many dictionary entries to be created vulnerabilityurl | 0 |
438,891 | 30,667,853,888 | IssuesEvent | 2023-07-25 19:45:38 | onnx/onnx-mlir | https://api.github.com/repos/onnx/onnx-mlir | opened | SupportedONNXOps-cpu.md missing unsupported attributes | documentation | Resize at https://github.com/onnx/onnx-mlir/blob/main/docs/SupportedONNXOps-cpu.md mentions a few unsupported modes but looking at the code, it appears only specific modes are supported. Documentation should be updated.
For example, based on the code I don't think `align_corners` would be valid for onnx-mlir but it exists in the ONNX Resize Op (https://github.com/onnx/onnx/blob/main/docs/Operators.md#Resize) | 1.0 | SupportedONNXOps-cpu.md missing unsupported attributes - Resize at https://github.com/onnx/onnx-mlir/blob/main/docs/SupportedONNXOps-cpu.md mentions a few unsupported modes but looking at the code, it appears only specific modes are supported. Documentation should be updated.
For example, based on the code I don't think `align_corners` would be valid for onnx-mlir but it exists in the ONNX Resize Op (https://github.com/onnx/onnx/blob/main/docs/Operators.md#Resize) | non_priority | supportedonnxops cpu md missing unsupported attributes resize at mentions a few unsupported modes but looking at the code it appears only specific modes are supported documentation should be updated for example based on the code i don t think align corners would be valid for onnx mlir but it exists in the onnx resize op | 0 |
235,264 | 18,045,651,685 | IssuesEvent | 2021-09-18 21:13:46 | Megasix/follow_up_app | https://api.github.com/repos/Megasix/follow_up_app | closed | Add Personal informations in read me | documentation | you can add your infos in the README.md, at least mark your name.
| 1.0 | Add Personal informations in read me - you can add your infos in the README.md, at least mark your name.
| non_priority | add personal informations in read me you can add your infos in the readme md at least mark your name | 0 |
68,906 | 7,113,602,682 | IssuesEvent | 2018-01-17 21:04:50 | 18F/doi-extractives-data | https://api.github.com/repos/18F/doi-extractives-data | opened | Test site without Javascript | type:testing | Opening this instead of #1710 — we should test how the site (especially Explore Data pages) behave if a user doesn't have Javascript enabled. | 1.0 | Test site without Javascript - Opening this instead of #1710 — we should test how the site (especially Explore Data pages) behave if a user doesn't have Javascript enabled. | non_priority | test site without javascript opening this instead of — we should test how the site especially explore data pages behave if a user doesn t have javascript enabled | 0 |
8,827 | 3,009,705,197 | IssuesEvent | 2015-07-28 08:30:36 | ufal/lindat-dspace | https://api.github.com/repos/ufal/lindat-dspace | reopened | An uploaded file doesn't immediately appear in uploaded file list | bug duplicate tested | During submission, uploading a file from file system succeeds but the latest uploaded file doesn't appear in the "Files Uploaded" list. Current workaround to see it is to manually refresh by pressing "Upload" step in progress list.
Uploading from URL works as expected though and the new file is immediately listed. | 1.0 | An uploaded file doesn't immediately appear in uploaded file list - During submission, uploading a file from file system succeeds but the latest uploaded file doesn't appear in the "Files Uploaded" list. Current workaround to see it is to manually refresh by pressing "Upload" step in progress list.
Uploading from URL works as expected though and the new file is immediately listed. | non_priority | an uploaded file doesn t immediately appear in uploaded file list during submission uploading a file from file system succeeds but the latest uploaded file doesn t appear in the files uploaded list current workaround to see it is to manually refresh by pressing upload step in progress list uploading from url works as expected though and the new file is immediately listed | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.