Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12
values | text_combine stringlengths 96 261k | label stringclasses 2
values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
18,976 | 13,507,434,496 | IssuesEvent | 2020-09-14 05:57:11 | joncampbell123/dosbox-x | https://api.github.com/repos/joncampbell123/dosbox-x | closed | Confusing "Quick right mouse button copy/paste" | usability |
**Is your feature request related to a problem? Please describe.**
https://github.com/joncampbell123/dosbox-x/blob/23653d031af2036b241d53bb94e548fff79a1ec7/CHANGELOG#L329
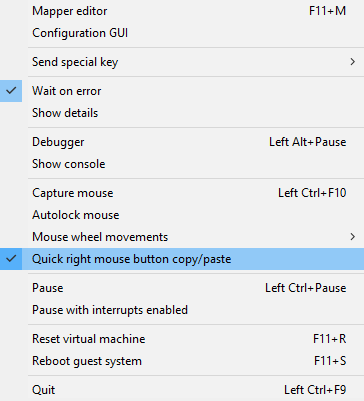
This is confus... | True | Confusing "Quick right mouse button copy/paste" -
**Is your feature request related to a problem? Please describe.**
https://github.com/joncampbell123/dosbox-x/blob/23653d031af2036b241d53bb94e548fff79a1ec7/CHANGELOG#L329
"<b>
... | 1.0 | Unable to Install my own SSL Certificate in "lago-api" Docker Container. - Hi,
I have deployed lago through Docker on my AWS EC2 Instance.
Now the problem is if I set my LAGO_FRONT_URL and LAGO_API_URL to my instance's public IPv4, I can succesfully login but cannot copy the api from the Copy API button. getting th... | non_priority | unable to install my own ssl certificate in lago api docker container hi i have deployed lago through docker on my aws instance now the problem is if i set my lago front url and lago api url to my instance s public i can succesfully login but cannot copy the api from the copy api button getting the err... | 0 |
388,676 | 26,777,600,660 | IssuesEvent | 2023-01-31 18:21:16 | uf-mil/mil | https://api.github.com/repos/uf-mil/mil | opened | Add note on receiving packages and sending info to Schwartz | documentation software difficulty: very easy | ### Assignee
_No response_
### Deadline
_No response_
### What needs to change?
Whenever a package is received in MIL, a note needs to be sent to Schwartz - a note on this should be added to the docs.
### How would this task be tested?
1. No testing - just add to docs.
### Contacts
- [ ] We need help from the ... | 1.0 | Add note on receiving packages and sending info to Schwartz - ### Assignee
_No response_
### Deadline
_No response_
### What needs to change?
Whenever a package is received in MIL, a note needs to be sent to Schwartz - a note on this should be added to the docs.
### How would this task be tested?
1. No testing -... | non_priority | add note on receiving packages and sending info to schwartz assignee no response deadline no response what needs to change whenever a package is received in mil a note needs to be sent to schwartz a note on this should be added to the docs how would this task be tested no testing ... | 0 |
301,448 | 22,756,998,663 | IssuesEvent | 2022-07-07 17:26:17 | dagster-io/dagster | https://api.github.com/repos/dagster-io/dagster | closed | Add migration guide to documentation | documentation | ## Advice
We would like to see a structured release planning and a guide\examples to upgrade the dagster platform in production, with major pitfalls covered.
## Ideas of Implementation
Add a session of migration guide in [releases chapter](https://docs.dagster.io/community/releases). | 1.0 | Add migration guide to documentation - ## Advice
We would like to see a structured release planning and a guide\examples to upgrade the dagster platform in production, with major pitfalls covered.
## Ideas of Implementation
Add a session of migration guide in [releases chapter](https://docs.dagster.io/communit... | non_priority | add migration guide to documentation advice we would like to see a structured release planning and a guide examples to upgrade the dagster platform in production with major pitfalls covered ideas of implementation add a session of migration guide in | 0 |
5,937 | 2,989,943,077 | IssuesEvent | 2015-07-21 05:05:38 | ecology-rocks/grammaR | https://api.github.com/repos/ecology-rocks/grammaR | opened | spinStory | documentation enhancement generalize testing | I just copied/pasted from the old stuff. Will need to generalize, test, document, etc. Probably take the write() out as default, since that's terrible practice. Also dangerous. | 1.0 | spinStory - I just copied/pasted from the old stuff. Will need to generalize, test, document, etc. Probably take the write() out as default, since that's terrible practice. Also dangerous. | non_priority | spinstory i just copied pasted from the old stuff will need to generalize test document etc probably take the write out as default since that s terrible practice also dangerous | 0 |
398,566 | 27,201,794,087 | IssuesEvent | 2023-02-20 10:14:19 | giantswarm/harbor-app | https://api.github.com/repos/giantswarm/harbor-app | closed | Documentation of operational information | documentation | We need to have some operational information available and updated:
- Disaster recovery of harbor
- Updating to a new version of harbor
- Recovering a failed deployment for harbor
- Debugging runtime issues (where to find logs, which info is exposed where) | 1.0 | Documentation of operational information - We need to have some operational information available and updated:
- Disaster recovery of harbor
- Updating to a new version of harbor
- Recovering a failed deployment for harbor
- Debugging runtime issues (where to find logs, which info is exposed where) | non_priority | documentation of operational information we need to have some operational information available and updated disaster recovery of harbor updating to a new version of harbor recovering a failed deployment for harbor debugging runtime issues where to find logs which info is exposed where | 0 |
104,987 | 13,152,284,058 | IssuesEvent | 2020-08-09 21:20:59 | merenlab/anvio | https://api.github.com/repos/merenlab/anvio | closed | genes_in_contigs table should have a "type" column, which states whether the gene is coding or non-coding | contigs database core design | In the current design, it is very hacky/difficult to work with gene collections when you want codon sequences and values like 'codon_order_in_gene' and 'base_pos_in_codon', because noncoding genes do not have these attributes. This issue is magnified greatly when external gene calls are imported during anvi-gen-contigs... | 1.0 | genes_in_contigs table should have a "type" column, which states whether the gene is coding or non-coding - In the current design, it is very hacky/difficult to work with gene collections when you want codon sequences and values like 'codon_order_in_gene' and 'base_pos_in_codon', because noncoding genes do not have the... | non_priority | genes in contigs table should have a type column which states whether the gene is coding or non coding in the current design it is very hacky difficult to work with gene collections when you want codon sequences and values like codon order in gene and base pos in codon because noncoding genes do not have the... | 0 |
30,790 | 11,849,415,471 | IssuesEvent | 2020-03-24 15:12:52 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Simplify or remove Kibana Privilege Calculator | Feature:Security/Feature Controls Team:Security chore | ## Background
The role management screen utilizes a Privilege Calculator in order to tell users what their effective privileges are for the role in question. It takes the following into account:
- Global Base Privileges
- Global Feature Privileges
- Space Base Privileges
- Space Feature Privileges
It curren... | True | Simplify or remove Kibana Privilege Calculator - ## Background
The role management screen utilizes a Privilege Calculator in order to tell users what their effective privileges are for the role in question. It takes the following into account:
- Global Base Privileges
- Global Feature Privileges
- Space Base Priv... | non_priority | simplify or remove kibana privilege calculator background the role management screen utilizes a privilege calculator in order to tell users what their effective privileges are for the role in question it takes the following into account global base privileges global feature privileges space base priv... | 0 |
345,967 | 30,856,780,967 | IssuesEvent | 2023-08-02 21:21:52 | istio/istio.io | https://api.github.com/repos/istio/istio.io | reopened | Performance doc charts are out of date. | area/test and release kind/docs lifecycle/stale | https://istio.io/latest/docs/ops/deployment/performance-and-scalability/
Docs use {{< istio_release_name >}} so they state 1.15.
Chart svgs were last updated for 1.8 https://github.com/istio/istio.io/pull/8574
The results in the text are likely out of date as well.
| 1.0 | Performance doc charts are out of date. - https://istio.io/latest/docs/ops/deployment/performance-and-scalability/
Docs use {{< istio_release_name >}} so they state 1.15.
Chart svgs were last updated for 1.8 https://github.com/istio/istio.io/pull/8574
The results in the text are likely out of date as well.
| non_priority | performance doc charts are out of date docs use so they state chart svgs were last updated for the results in the text are likely out of date as well | 0 |
26,752 | 5,284,723,939 | IssuesEvent | 2017-02-08 01:26:53 | simplabs/ember-simple-auth | https://api.github.com/repos/simplabs/ember-simple-auth | closed | Feature request - Add demo app | documentation | Hi,
I have been doing a demo app for 0.8.0 version of ESA with a "devise" backend.
Do you plan to add some examples or demo apps inside the repo for the 1.0 version?
I would be interested in helping with this.
| 1.0 | Feature request - Add demo app - Hi,
I have been doing a demo app for 0.8.0 version of ESA with a "devise" backend.
Do you plan to add some examples or demo apps inside the repo for the 1.0 version?
I would be interested in helping with this.
| non_priority | feature request add demo app hi i have been doing a demo app for version of esa with a devise backend do you plan to add some examples or demo apps inside the repo for the version i would be interested in helping with this | 0 |
100,391 | 30,692,602,122 | IssuesEvent | 2023-07-26 16:08:21 | metabase/metabase | https://api.github.com/repos/metabase/metabase | opened | Get the CLJS REPL connecting to Metabase running in the browser | Type:Bug .Building & Releasing .Team/QueryProcessor :hammer_and_wrench: | ### Describe the bug
When working in the CLJS environment, the Node REPL runs in its own world, separate from the browser. Some functionality doesn't work at all there (the DOM for example), and other things are different from the browser environment.
One notable gap is that `metabase.lib.core` doesn't work at all ... | 1.0 | Get the CLJS REPL connecting to Metabase running in the browser - ### Describe the bug
When working in the CLJS environment, the Node REPL runs in its own world, separate from the browser. Some functionality doesn't work at all there (the DOM for example), and other things are different from the browser environment.
... | non_priority | get the cljs repl connecting to metabase running in the browser describe the bug when working in the cljs environment the node repl runs in its own world separate from the browser some functionality doesn t work at all there the dom for example and other things are different from the browser environment ... | 0 |
16,674 | 5,270,776,246 | IssuesEvent | 2017-02-06 07:02:40 | learning-unlimited/ESP-Website | https://api.github.com/repos/learning-unlimited/ESP-Website | closed | select_students is bitrotted | Old/unused code | It tries to interact with some weird caching stuff that was deleted from ClassSection years ago, and apparently nobody noticed. We should delete it. | 1.0 | select_students is bitrotted - It tries to interact with some weird caching stuff that was deleted from ClassSection years ago, and apparently nobody noticed. We should delete it. | non_priority | select students is bitrotted it tries to interact with some weird caching stuff that was deleted from classsection years ago and apparently nobody noticed we should delete it | 0 |
247,700 | 26,728,765,941 | IssuesEvent | 2023-01-30 01:04:09 | ThomasRuemmler/openspaceplanner | https://api.github.com/repos/ThomasRuemmler/openspaceplanner | opened | CVE-2022-48285 (Medium) detected in jszip-3.1.5.tgz | security vulnerability | ## CVE-2022-48285 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jszip-3.1.5.tgz</b></p></summary>
<p>Create, read and edit .zip files with JavaScript http://stuartk.com/jszip</p>
<... | True | CVE-2022-48285 (Medium) detected in jszip-3.1.5.tgz - ## CVE-2022-48285 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jszip-3.1.5.tgz</b></p></summary>
<p>Create, read and edit .zi... | non_priority | cve medium detected in jszip tgz cve medium severity vulnerability vulnerable library jszip tgz create read and edit zip files with javascript library home page a href path to dependency file web package json path to vulnerable library web node modules jszip pac... | 0 |
143,168 | 19,143,230,858 | IssuesEvent | 2021-12-02 02:55:59 | n-devs/edit-map | https://api.github.com/repos/n-devs/edit-map | opened | CVE-2021-29059 (High) detected in is-svg-2.1.0.tgz | security vulnerability | ## CVE-2021-29059 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>is-svg-2.1.0.tgz</b></p></summary>
<p>Check if a string or buffer is SVG</p>
<p>Library home page: <a href="https://re... | True | CVE-2021-29059 (High) detected in is-svg-2.1.0.tgz - ## CVE-2021-29059 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>is-svg-2.1.0.tgz</b></p></summary>
<p>Check if a string or buffer... | non_priority | cve high detected in is svg tgz cve high severity vulnerability vulnerable library is svg tgz check if a string or buffer is svg library home page a href path to dependency file edit map package json path to vulnerable library edit map node modules is svg pa... | 0 |
166,120 | 26,284,886,089 | IssuesEvent | 2023-01-07 18:20:14 | edenia/eden-spend-explorer | https://api.github.com/repos/edenia/eden-spend-explorer | closed | Check the margin space of the charts | enhancement UI / UX Design | **Description and expected**
We need to resize the margin spaces between the charts. This will give the user more breath when observe the information | 1.0 | Check the margin space of the charts - **Description and expected**
We need to resize the margin spaces between the charts. This will give the user more breath when observe the information | non_priority | check the margin space of the charts description and expected we need to resize the margin spaces between the charts this will give the user more breath when observe the information | 0 |
52,780 | 13,050,473,908 | IssuesEvent | 2020-07-29 15:32:54 | golang/go | https://api.github.com/repos/golang/go | closed | x/build/cmd/releasebot: remove obsolete check that the major version is listed on the project page | Builders NeedsFix release-blocker | The https://golang.org/project/ page has a "Version history" section that lists major Go releases that have been released. Prior to [CL 229483](https://golang.org/cl/229483), it needed to be manually updated before each final major release, and so to catch potential mistakes releasebot has a safety check that aborts th... | 1.0 | x/build/cmd/releasebot: remove obsolete check that the major version is listed on the project page - The https://golang.org/project/ page has a "Version history" section that lists major Go releases that have been released. Prior to [CL 229483](https://golang.org/cl/229483), it needed to be manually updated before each... | non_priority | x build cmd releasebot remove obsolete check that the major version is listed on the project page the page has a version history section that lists major go releases that have been released prior to it needed to be manually updated before each final major release and so to catch potential mistakes releaseb... | 0 |
139,055 | 18,836,336,409 | IssuesEvent | 2021-11-11 01:39:59 | ElliotChen/spring_boot_example | https://api.github.com/repos/ElliotChen/spring_boot_example | opened | CVE-2021-38153 (Medium) detected in kafka-clients-2.7.1.jar | security vulnerability | ## CVE-2021-38153 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>kafka-clients-2.7.1.jar</b></p></summary>
<p></p>
<p>Library home page: <a href="https://kafka.apache.org">https://k... | True | CVE-2021-38153 (Medium) detected in kafka-clients-2.7.1.jar - ## CVE-2021-38153 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>kafka-clients-2.7.1.jar</b></p></summary>
<p></p>
<p>L... | non_priority | cve medium detected in kafka clients jar cve medium severity vulnerability vulnerable library kafka clients jar library home page a href path to dependency file spring boot example pom xml path to vulnerable library home wss scanner repository org apache kafka... | 0 |
347,946 | 24,904,603,997 | IssuesEvent | 2022-10-29 04:33:04 | CHAMPION316/coffee-forest | https://api.github.com/repos/CHAMPION316/coffee-forest | closed | GENERAL: Creating less padding on about.html | documentation could have | Too much padding is causing the test to be too centered. Decrease padding for better viewability. | 1.0 | GENERAL: Creating less padding on about.html - Too much padding is causing the test to be too centered. Decrease padding for better viewability. | non_priority | general creating less padding on about html too much padding is causing the test to be too centered decrease padding for better viewability | 0 |
64,515 | 12,474,824,755 | IssuesEvent | 2020-05-29 10:21:55 | WesselSmit/education-portal | https://api.github.com/repos/WesselSmit/education-portal | closed | Build new mobile/tablet menu (with toggle?) | code design wontfix | Build the new menu design if the user tests are positive | 1.0 | Build new mobile/tablet menu (with toggle?) - Build the new menu design if the user tests are positive | non_priority | build new mobile tablet menu with toggle build the new menu design if the user tests are positive | 0 |
33,493 | 7,132,454,114 | IssuesEvent | 2018-01-22 14:40:17 | primefaces/primeng | https://api.github.com/repos/primefaces/primeng | closed | onLazyLoad event not fired when a text filter is cleared out | defect | ```
[X] bug report => Search github for a similar issue or PR before submitting
[ ] feature request => Please check if request is not on the roadmap already https://github.com/primefaces/primeng/wiki/Roadmap
[ ] support request => Please do not submit support request here, instead see http://forum.primefaces.org/vie... | 1.0 | onLazyLoad event not fired when a text filter is cleared out - ```
[X] bug report => Search github for a similar issue or PR before submitting
[ ] feature request => Please check if request is not on the roadmap already https://github.com/primefaces/primeng/wiki/Roadmap
[ ] support request => Please do not submit su... | non_priority | onlazyload event not fired when a text filter is cleared out bug report search github for a similar issue or pr before submitting feature request please check if request is not on the roadmap already support request please do not submit support request here instead see current beh... | 0 |
33,938 | 12,229,047,999 | IssuesEvent | 2020-05-03 22:10:21 | YANG-DB/yang-db | https://api.github.com/repos/YANG-DB/yang-db | opened | CVE-2020-11111 (High) detected in jackson-databind-2.9.8.jar | security vulnerability | ## CVE-2020-11111 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2020-11111 (High) detected in jackson-databind-2.9.8.jar - ## CVE-2020-11111 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General... | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to vulnerable library yang db distrib dragon drag... | 0 |
222,948 | 17,514,208,588 | IssuesEvent | 2021-08-11 03:44:31 | pingcap/ticdc | https://api.github.com/repos/pingcap/ticdc | closed | Capture list increased 1 unexpected after all PD restarting | type/bug component/status-server difficulty/easy severity/minor bug-from-internal-test | ## Bug Report
Please answer these questions before submitting your issue. Thanks!
1. What did you do? If possible, provide a recipe for reproducing the error.
- 2x capture:
Starting component `cdc`: /root/.tiup/components/cdc/v5.1.0/cdc cli capture list --pd=http://172.16.6.24:2379
[
{
"id": "3378b... | 1.0 | Capture list increased 1 unexpected after all PD restarting - ## Bug Report
Please answer these questions before submitting your issue. Thanks!
1. What did you do? If possible, provide a recipe for reproducing the error.
- 2x capture:
Starting component `cdc`: /root/.tiup/components/cdc/v5.1.0/cdc cli captu... | non_priority | capture list increased unexpected after all pd restarting bug report please answer these questions before submitting your issue thanks what did you do if possible provide a recipe for reproducing the error capture starting component cdc root tiup components cdc cdc cli capture... | 0 |
26,213 | 4,622,767,866 | IssuesEvent | 2016-09-27 08:46:29 | siddhartha-gadgil/ProvingGround | https://api.github.com/repos/siddhartha-gadgil/ProvingGround | closed | Very poor performance due to cascade of replacements. | defect | In generating from _Monoids_, but not from just _logic_, there is a huge slowdown, with most of the time spent in replace methods. This appears to be because:
* for the sake of safety, lambdas:
* create an inner variable
* in the case of lambda-fixed, check independence.
* both these involve replace... | 1.0 | Very poor performance due to cascade of replacements. - In generating from _Monoids_, but not from just _logic_, there is a huge slowdown, with most of the time spent in replace methods. This appears to be because:
* for the sake of safety, lambdas:
* create an inner variable
* in the case of lambda-... | non_priority | very poor performance due to cascade of replacements in generating from monoids but not from just logic there is a huge slowdown with most of the time spent in replace methods this appears to be because for the sake of safety lambdas create an inner variable in the case of lambda ... | 0 |
106,223 | 9,122,408,375 | IssuesEvent | 2019-02-23 07:39:25 | ChrisCScott/forecaster | https://api.github.com/repos/ChrisCScott/forecaster | closed | Add tests for SubForecast subclasses | ContributionForecast Forecast IncomeForecast LivingExpensesForecast ReductionForecast SubForecast TaxForecast WithdrawalForecast tests | With `IncomeForecast`, `LivingExpensesForecast`, `ReductionForecast` (rename this `LifecycleForecast`?), `ContributionForecast`, `WithdrawalForecast`, and `TaxForecast` now implemented, we need to test them (or, in the cast of `IncomeForecast`, reimplement its tests).
Thanks to relatively rigorous encapsulation (pen... | 1.0 | Add tests for SubForecast subclasses - With `IncomeForecast`, `LivingExpensesForecast`, `ReductionForecast` (rename this `LifecycleForecast`?), `ContributionForecast`, `WithdrawalForecast`, and `TaxForecast` now implemented, we need to test them (or, in the cast of `IncomeForecast`, reimplement its tests).
Thanks to... | non_priority | add tests for subforecast subclasses with incomeforecast livingexpensesforecast reductionforecast rename this lifecycleforecast contributionforecast withdrawalforecast and taxforecast now implemented we need to test them or in the cast of incomeforecast reimplement its tests thanks to... | 0 |
19,500 | 3,774,201,492 | IssuesEvent | 2016-03-17 08:03:23 | quantmind/pulsar | https://api.github.com/repos/quantmind/pulsar | closed | Exception message in tests | test won't fix | In `tests/async/events.py` we see at line 24 the line
h.bind_event('finish', lambda f, exc=None: 'OK'+4)
This raises exceptions, which result in the unintelligible output `"Exception ignored in:"` in the middle of the test output stream. If it's intended to raise that exception, could the message be suppresse... | 1.0 | Exception message in tests - In `tests/async/events.py` we see at line 24 the line
h.bind_event('finish', lambda f, exc=None: 'OK'+4)
This raises exceptions, which result in the unintelligible output `"Exception ignored in:"` in the middle of the test output stream. If it's intended to raise that exception, c... | non_priority | exception message in tests in tests async events py we see at line the line h bind event finish lambda f exc none ok this raises exceptions which result in the unintelligible output exception ignored in in the middle of the test output stream if it s intended to raise that exception co... | 0 |
109,895 | 16,903,293,840 | IssuesEvent | 2021-06-24 02:02:46 | turkdevops/teletype | https://api.github.com/repos/turkdevops/teletype | closed | CVE-2021-33502 (High) detected in normalize-url-4.5.0.tgz - autoclosed | security vulnerability | ## CVE-2021-33502 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>normalize-url-4.5.0.tgz</b></p></summary>
<p>Normalize a URL</p>
<p>Library home page: <a href="https://registry.npmjs... | True | CVE-2021-33502 (High) detected in normalize-url-4.5.0.tgz - autoclosed - ## CVE-2021-33502 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>normalize-url-4.5.0.tgz</b></p></summary>
<p>... | non_priority | cve high detected in normalize url tgz autoclosed cve high severity vulnerability vulnerable library normalize url tgz normalize a url library home page a href path to dependency file teletype package json path to vulnerable library teletype node modules normalize ... | 0 |
166,123 | 12,891,369,249 | IssuesEvent | 2020-07-13 17:36:27 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: sysbench/oltp_write_only/nodes=3/cpu=32/conc=128 failed | C-test-failure O-roachtest O-robot branch-master release-blocker | [(roachtest).sysbench/oltp_write_only/nodes=3/cpu=32/conc=128 failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2079204&tab=buildLog) on [master@542c83e7db1694208e09c7fea7d350db4993b897](https://github.com/cockroachdb/cockroach/commits/542c83e7db1694208e09c7fea7d350db4993b897):
```
| signal: killed
... | 2.0 | roachtest: sysbench/oltp_write_only/nodes=3/cpu=32/conc=128 failed - [(roachtest).sysbench/oltp_write_only/nodes=3/cpu=32/conc=128 failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2079204&tab=buildLog) on [master@542c83e7db1694208e09c7fea7d350db4993b897](https://github.com/cockroachdb/cockroach/commits/542... | non_priority | roachtest sysbench oltp write only nodes cpu conc failed on signal killed signal killed error types exec exiterror wraps context canceled error types withstack withstack safedetails withsafedetails errutil withmessage main withcommanddeta... | 0 |
32,039 | 13,751,942,517 | IssuesEvent | 2020-10-06 13:57:09 | terraform-providers/terraform-provider-aws | https://api.github.com/repos/terraform-providers/terraform-provider-aws | closed | aws_dynamodb_table returns name before resource is even created | bug service/dynamodb upstream-terraform | <!---
Please note the following potential times when an issue might be in Terraform core:
* [Configuration Language](https://www.terraform.io/docs/configuration/index.html) or resource ordering issues
* [State](https://www.terraform.io/docs/state/index.html) and [State Backend](https://www.terraform.io/docs/backen... | 1.0 | aws_dynamodb_table returns name before resource is even created - <!---
Please note the following potential times when an issue might be in Terraform core:
* [Configuration Language](https://www.terraform.io/docs/configuration/index.html) or resource ordering issues
* [State](https://www.terraform.io/docs/state/in... | non_priority | aws dynamodb table returns name before resource is even created please note the following potential times when an issue might be in terraform core or resource ordering issues and issues issues issues spans resources across multiple providers if you are running into one ... | 0 |
54,860 | 23,346,038,637 | IssuesEvent | 2022-08-09 18:04:16 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | closed | Explore React Testing Library for testing React components and web maps | Service: Dev Type: Research | **Docs and videos**
- https://testing-library.com/docs/react-testing-library/intro/
- https://blog.sapegin.me/all/react-testing-3-jest-and-react-testing-library/
- https://www.youtube.com/watch?v=7dTTFW7yACQ
- https://github.com/visgl/react-map-gl/issues/210
- https://blog.wick.technology/testing-react-map/
- htt... | 1.0 | Explore React Testing Library for testing React components and web maps - **Docs and videos**
- https://testing-library.com/docs/react-testing-library/intro/
- https://blog.sapegin.me/all/react-testing-3-jest-and-react-testing-library/
- https://www.youtube.com/watch?v=7dTTFW7yACQ
- https://github.com/visgl/react-m... | non_priority | explore react testing library for testing react components and web maps docs and videos goal add tests to the pr that i ve been working on to refactor the user management features in moped editor stretch goal circle back on the tests for the moped api and refresh myself on ... | 0 |
171,631 | 20,984,629,066 | IssuesEvent | 2022-03-29 00:49:42 | fdm-monster/fdm-monster-client | https://api.github.com/repos/fdm-monster/fdm-monster-client | opened | cypress-9.5.3.tgz: 1 vulnerabilities (highest severity is: 7.5) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>cypress-9.5.3.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/qs/package.json</p>
<p>
<p>Fo... | True | cypress-9.5.3.tgz: 1 vulnerabilities (highest severity is: 7.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>cypress-9.5.3.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to... | non_priority | cypress tgz vulnerabilities highest severity is vulnerable library cypress tgz path to dependency file package json path to vulnerable library node modules qs package json found in head commit a href vulnerabilities cve severity cvss dependency ty... | 0 |
65,036 | 7,854,315,123 | IssuesEvent | 2018-06-20 20:21:43 | Azure/azure-functions-ux | https://api.github.com/repos/Azure/azure-functions-ux | closed | Validate Azure Files storage account | Runtime pending-design | Today, if a customer deletes the storage account backing the content share, the function app is left in a broken state and the portal doesn't show any information about what is going on.
It would be good if the portal could validate the storage account when failures to talk to Kudu occur (calls to getfunctions, etc)... | 1.0 | Validate Azure Files storage account - Today, if a customer deletes the storage account backing the content share, the function app is left in a broken state and the portal doesn't show any information about what is going on.
It would be good if the portal could validate the storage account when failures to talk to ... | non_priority | validate azure files storage account today if a customer deletes the storage account backing the content share the function app is left in a broken state and the portal doesn t show any information about what is going on it would be good if the portal could validate the storage account when failures to talk to ... | 0 |
67,162 | 9,011,405,489 | IssuesEvent | 2019-02-05 14:37:28 | Braeden261/kendoSchool | https://api.github.com/repos/Braeden261/kendoSchool | closed | KG-03: Define High Level Resource Plan | Documentation | Use the Estimation Spreadsheet to put a rough plan together for the hours required each week to achieve MVP goals. | 1.0 | KG-03: Define High Level Resource Plan - Use the Estimation Spreadsheet to put a rough plan together for the hours required each week to achieve MVP goals. | non_priority | kg define high level resource plan use the estimation spreadsheet to put a rough plan together for the hours required each week to achieve mvp goals | 0 |
98,539 | 20,752,707,398 | IssuesEvent | 2022-03-15 09:17:01 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | New Menu Item Error: 0 array_key_exists(): Argument #2 ($array) must be of type array, stdClass given | No Code Attached Yet | ### Steps to reproduce the issue
With PHP8 (8.0.8, 8.1.0) I get the above error when i try to add a new menu item
With PHP7 (7.4.28) all works fine
### Expected result
### Actual result
### System information (as much as possible)
Setting Value
PHP Built On Linux
Database Type mysql
Databas... | 1.0 | New Menu Item Error: 0 array_key_exists(): Argument #2 ($array) must be of type array, stdClass given - ### Steps to reproduce the issue
With PHP8 (8.0.8, 8.1.0) I get the above error when i try to add a new menu item
With PHP7 (7.4.28) all works fine
### Expected result
### Actual result
### System ... | non_priority | new menu item error array key exists argument array must be of type array stdclass given steps to reproduce the issue with i get the above error when i try to add a new menu item with all works fine expected result actual result system informa... | 0 |
76,220 | 9,922,959,424 | IssuesEvent | 2019-07-01 05:29:12 | Alexander-Miller/treemacs | https://api.github.com/repos/Alexander-Miller/treemacs | closed | Split readme keymap section | Documentation Enhancement | Now that the keybindings are split over several maps the readme should do the same. | 1.0 | Split readme keymap section - Now that the keybindings are split over several maps the readme should do the same. | non_priority | split readme keymap section now that the keybindings are split over several maps the readme should do the same | 0 |
2,547 | 8,675,068,872 | IssuesEvent | 2018-11-30 09:48:02 | citrusframework/citrus | https://api.github.com/repos/citrusframework/citrus | opened | Breaking change in waitFor().message() | Prio: High READY Type: Maintainance | **Citrus Version**
>= 2.7.7
**Description**
If you upgrade your Citrus version to 2.7.7 or higher, we've a breaking change in the http wait builder API. We'll correct this with one of the future releases to ensure effortless version upgrades
**API before change**
```java
waitFor().message("message");
``... | True | Breaking change in waitFor().message() - **Citrus Version**
>= 2.7.7
**Description**
If you upgrade your Citrus version to 2.7.7 or higher, we've a breaking change in the http wait builder API. We'll correct this with one of the future releases to ensure effortless version upgrades
**API before change**
``... | non_priority | breaking change in waitfor message citrus version description if you upgrade your citrus version to or higher we ve a breaking change in the http wait builder api we ll correct this with one of the future releases to ensure effortless version upgrades api before change ... | 0 |
11,474 | 9,376,843,829 | IssuesEvent | 2019-04-04 08:56:35 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | When using a User Assigned Managed identity, SQL login fails when the identity is assigned to an Active Directory Group | app-service-web/svc cxp in-progress product-question sql-database/svc triaged | I'm using a User assigned managed identity assigned to an AAD Group. This group is then in turn assigned to the Azure SQL Database using the CREATE USER FROM EXTERNAL PROVIDER call as above. Attempting to connect to the database via a .net core 2.2 application results in SqlException: Login failed for user '<UPN>... | 1.0 | When using a User Assigned Managed identity, SQL login fails when the identity is assigned to an Active Directory Group - I'm using a User assigned managed identity assigned to an AAD Group. This group is then in turn assigned to the Azure SQL Database using the CREATE USER FROM EXTERNAL PROVIDER call as above. Attempt... | non_priority | when using a user assigned managed identity sql login fails when the identity is assigned to an active directory group i m using a user assigned managed identity assigned to an aad group this group is then in turn assigned to the azure sql database using the create user from external provider call as above attempt... | 0 |
36,630 | 12,418,153,420 | IssuesEvent | 2020-05-22 23:01:13 | wrbejar/wrbejar-Nova8Ksa | https://api.github.com/repos/wrbejar/wrbejar-Nova8Ksa | opened | CVE-2016-1000031 (High) detected in commons-fileupload-1.2.2.jar | security vulnerability | ## CVE-2016-1000031 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-fileupload-1.2.2.jar</b></p></summary>
<p>The FileUpload component provides a simple yet flexible means of a... | True | CVE-2016-1000031 (High) detected in commons-fileupload-1.2.2.jar - ## CVE-2016-1000031 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-fileupload-1.2.2.jar</b></p></summary>
<p... | non_priority | cve high detected in commons fileupload jar cve high severity vulnerability vulnerable library commons fileupload jar the fileupload component provides a simple yet flexible means of adding support for multipart file upload functionality to servlets and web applications p... | 0 |
172,064 | 27,229,461,608 | IssuesEvent | 2023-02-21 12:09:18 | ProgrammingPhilippines/project_rei | https://api.github.com/repos/ProgrammingPhilippines/project_rei | opened | Shop Module & Game Economics | 🎯 Gameplay 💻 Engineering 💬 User Interface 🗯 User Experience 🖼 Game Design | We'll need to implement a shop system that will sell "items" to the player for upgrades, consumables/useables, weapons. This will function similar to an inventory system.
We'll also need to implement currency that goes with purchasing items. | 1.0 | Shop Module & Game Economics - We'll need to implement a shop system that will sell "items" to the player for upgrades, consumables/useables, weapons. This will function similar to an inventory system.
We'll also need to implement currency that goes with purchasing items. | non_priority | shop module game economics we ll need to implement a shop system that will sell items to the player for upgrades consumables useables weapons this will function similar to an inventory system we ll also need to implement currency that goes with purchasing items | 0 |
67,955 | 8,204,155,841 | IssuesEvent | 2018-09-03 04:40:58 | brave/browser-laptop | https://api.github.com/repos/brave/browser-laptop | closed | Tab opening enhancement | design feature/tab-page feature/tabsbar stale suggestion | ### Description
This happens when you're on the last tab at 1st page, and every new tab would be opening on the page 2 (http://prntscr.com/hxmhwm).
If you start opening new tabs from the last tab on page 1, you will know only if the first one opened successfully because an arrow will appear at the end of tab bar.
Bu... | 1.0 | Tab opening enhancement - ### Description
This happens when you're on the last tab at 1st page, and every new tab would be opening on the page 2 (http://prntscr.com/hxmhwm).
If you start opening new tabs from the last tab on page 1, you will know only if the first one opened successfully because an arrow will appear ... | non_priority | tab opening enhancement description this happens when you re on the last tab at page and every new tab would be opening on the page if you start opening new tabs from the last tab on page you will know only if the first one opened successfully because an arrow will appear at the end of tab bar but ... | 0 |
385,303 | 26,630,331,527 | IssuesEvent | 2023-01-24 17:20:06 | eclipse/lsp4jakarta | https://api.github.com/repos/eclipse/lsp4jakarta | closed | Document what is supported in which release of LSP4Jakarta | documentation | Document or at least summarise what capabilities (coding assistance) are supported in which release of LSP4Jakarta.
e.g., translate what is captured in https://github.com/eclipse/lsp4jakarta/issues/16 to an end-user (developer) consumable information mapping to the corresponding release(s) of the language server. | 1.0 | Document what is supported in which release of LSP4Jakarta - Document or at least summarise what capabilities (coding assistance) are supported in which release of LSP4Jakarta.
e.g., translate what is captured in https://github.com/eclipse/lsp4jakarta/issues/16 to an end-user (developer) consumable information mappi... | non_priority | document what is supported in which release of document or at least summarise what capabilities coding assistance are supported in which release of e g translate what is captured in to an end user developer consumable information mapping to the corresponding release s of the language server | 0 |
27,347 | 11,473,741,583 | IssuesEvent | 2020-02-10 01:00:13 | whitesource-yossi/datahelix | https://api.github.com/repos/whitesource-yossi/datahelix | opened | CVE-2017-18640 (High) detected in snakeyaml-1.23.jar | security vulnerability | ## CVE-2017-18640 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snakeyaml-1.23.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http:/... | True | CVE-2017-18640 (High) detected in snakeyaml-1.23.jar - ## CVE-2017-18640 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snakeyaml-1.23.jar</b></p></summary>
<p>YAML 1.1 parser and emi... | non_priority | cve high detected in snakeyaml jar cve high severity vulnerability vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file tmp ws scm datahelix core build gradle path to vulnerable library tmp ws ua downloa... | 0 |
189,373 | 15,186,899,772 | IssuesEvent | 2021-02-15 13:03:45 | arturo-lang/arturo | https://api.github.com/repos/arturo-lang/arturo | closed | [Sets\union] add example for documentation | documentation easy library todo | [Sets\union] add example for documentation
https://github.com/arturo-lang/arturo/blob/de6b44acd21e2d88248ccc42e565c2fabc5637a5/src/library/Sets.nim#L90
```text
# (c) 2019-2021 Yanis Zafirópulos
#
# @file: library/Sets.nim
######################################################
#=======================================... | 1.0 | [Sets\union] add example for documentation - [Sets\union] add example for documentation
https://github.com/arturo-lang/arturo/blob/de6b44acd21e2d88248ccc42e565c2fabc5637a5/src/library/Sets.nim#L90
```text
# (c) 2019-2021 Yanis Zafirópulos
#
# @file: library/Sets.nim
###################################################... | non_priority | add example for documentation add example for documentation text c yanis zafirópulos file library sets nim pragmas used ... | 0 |
173,842 | 21,182,114,020 | IssuesEvent | 2022-04-08 08:58:55 | OTTIN-T/OttinTimothe_5_27112020 | https://api.github.com/repos/OTTIN-T/OttinTimothe_5_27112020 | closed | WS-2019-0605 (Medium) detected in CSS::Sassv3.4.11 - autoclosed | security vulnerability | ## WS-2019-0605 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>CSS::Sassv3.4.11</b></p></summary>
<p>
<p>Library home page: <a href=https://metacpan.org/pod/CSS::Sass>https://metacp... | True | WS-2019-0605 (Medium) detected in CSS::Sassv3.4.11 - autoclosed - ## WS-2019-0605 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>CSS::Sassv3.4.11</b></p></summary>
<p>
<p>Library ho... | non_priority | ws medium detected in css autoclosed ws medium severity vulnerability vulnerable library css library home page a href found in base branch main vulnerable source files node modules node sass src libsass src lexer cpp ... | 0 |
62,147 | 15,170,050,117 | IssuesEvent | 2021-02-12 22:21:44 | lbl-srg/modelica-buildings | https://api.github.com/repos/lbl-srg/modelica-buildings | opened | Add default vendor annotation to generate point list | OpenBuildingControl | This issue is to add vendor annotation to the cdl control sequences, for generating point list. See [section 7.7.4 Point list](http://obc.lbl.gov/specification/cdl.html#point-list) of OBC specification. | 1.0 | Add default vendor annotation to generate point list - This issue is to add vendor annotation to the cdl control sequences, for generating point list. See [section 7.7.4 Point list](http://obc.lbl.gov/specification/cdl.html#point-list) of OBC specification. | non_priority | add default vendor annotation to generate point list this issue is to add vendor annotation to the cdl control sequences for generating point list see of obc specification | 0 |
50,934 | 7,644,731,498 | IssuesEvent | 2018-05-08 16:18:39 | dealii/dealii | https://api.github.com/repos/dealii/dealii | closed | Review all documentation related to GridGenerator | Documentation Manifold Meta Triangulation | GridGenerator functions have changed their default behaviour.
This should be reflected anywhere we discuss about manifold descriptions (e.g., tutorials, modules, etc.). | 1.0 | Review all documentation related to GridGenerator - GridGenerator functions have changed their default behaviour.
This should be reflected anywhere we discuss about manifold descriptions (e.g., tutorials, modules, etc.). | non_priority | review all documentation related to gridgenerator gridgenerator functions have changed their default behaviour this should be reflected anywhere we discuss about manifold descriptions e g tutorials modules etc | 0 |
22,170 | 10,731,372,471 | IssuesEvent | 2019-10-28 19:24:18 | melsorg/github-scanner-test | https://api.github.com/repos/melsorg/github-scanner-test | opened | CVE-2014-3509 (Medium) detected in openssl-OpenSSL_1_0_1 | security vulnerability | ## CVE-2014-3509 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opensslOpenSSL_1_0_1</b></p></summary>
<p>
<p>Akamai fork of openssl master.</p>
<p>Library home page: <a href=https:... | True | CVE-2014-3509 (Medium) detected in openssl-OpenSSL_1_0_1 - ## CVE-2014-3509 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opensslOpenSSL_1_0_1</b></p></summary>
<p>
<p>Akamai fork ... | non_priority | cve medium detected in openssl openssl cve medium severity vulnerability vulnerable library opensslopenssl akamai fork of openssl master library home page a href found in head commit a href library source files the source files were matched ... | 0 |
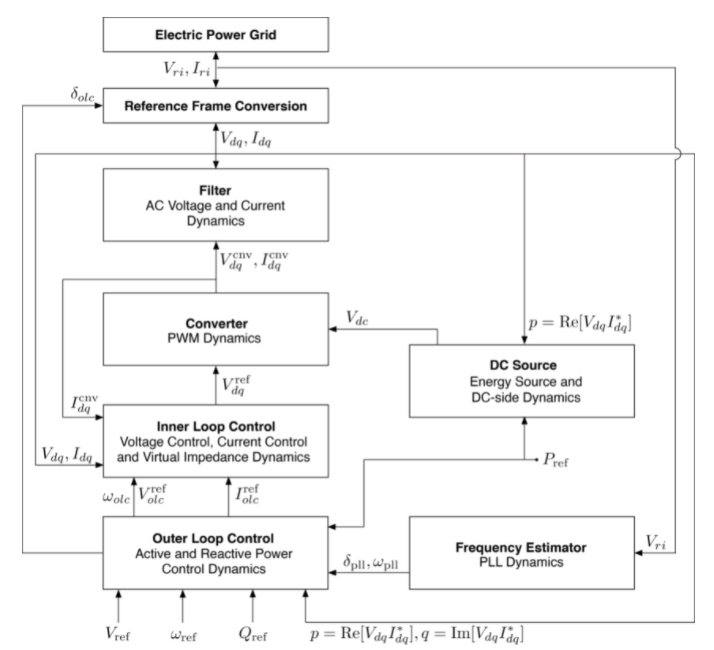
224,271 | 17,170,789,792 | IssuesEvent | 2021-07-15 03:54:33 | NREL-SIIP/PowerSimulationsDynamics.jl | https://api.github.com/repos/NREL-SIIP/PowerSimulationsDynamics.jl | closed | Inconsistent label for outer control angle | documentation | In the meta-model figure, the angle appears as δ<sub>olc</sub>, in the Virtual inertia model it appears as δθ<sub>olc</sub>, and in the Droop model it appears as θ<sub>olc</sub>:
 detected in linux-stable-rtv4.1.33 | Mend: dependency security vulnerability | ## CVE-2020-0431 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home pa... | True | CVE-2020-0431 (Medium) detected in linux-stable-rtv4.1.33 - ## CVE-2020-0431 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Car... | non_priority | cve medium detected in linux stable cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source f... | 0 |
157,624 | 13,697,709,992 | IssuesEvent | 2020-10-01 03:51:47 | msandfor/10-Easy-Steps | https://api.github.com/repos/msandfor/10-Easy-Steps | closed | [Bug]: Broken Links in emoji-key.md | documentation :memo: good first issue hacktoberfest :children_crossing: | **Describe the bug**
The links redirect to 404 page
**To Reproduce**
Steps to reproduce the behavior:
1. Go to '10-Easy-Steps/docs/emoji-key.md'
3. Scroll down to 'What's next'
4. Click on 'Notes for repository maintainers' and 'Automating the process using tools'
**Expected behavior**
Clicking on these li... | 1.0 | [Bug]: Broken Links in emoji-key.md - **Describe the bug**
The links redirect to 404 page
**To Reproduce**
Steps to reproduce the behavior:
1. Go to '10-Easy-Steps/docs/emoji-key.md'
3. Scroll down to 'What's next'
4. Click on 'Notes for repository maintainers' and 'Automating the process using tools'
**Exp... | non_priority | broken links in emoji key md describe the bug the links redirect to page to reproduce steps to reproduce the behavior go to easy steps docs emoji key md scroll down to what s next click on notes for repository maintainers and automating the process using tools expected b... | 0 |
258,559 | 27,564,311,386 | IssuesEvent | 2023-03-08 01:43:10 | cluesblues/didactic-pancake | https://api.github.com/repos/cluesblues/didactic-pancake | opened | CVE-2021-23337 (High) detected in lodash-4.17.4.tgz, lodash-1.3.1.tgz | security vulnerability | ## CVE-2021-23337 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-4.17.4.tgz</b>, <b>lodash-1.3.1.tgz</b></p></summary>
<p>
<details><summary><b>lodash-4.17.4.tgz</b></p></sum... | True | CVE-2021-23337 (High) detected in lodash-4.17.4.tgz, lodash-1.3.1.tgz - ## CVE-2021-23337 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-4.17.4.tgz</b>, <b>lodash-1.3.1.tgz</b... | non_priority | cve high detected in lodash tgz lodash tgz cve high severity vulnerability vulnerable libraries lodash tgz lodash tgz lodash tgz lodash modular utilities library home page a href path to dependency file package json path to vulnerable ... | 0 |
154,963 | 12,235,064,961 | IssuesEvent | 2020-05-04 14:21:40 | WoWManiaUK/Blackwing-Lair | https://api.github.com/repos/WoWManiaUK/Blackwing-Lair | opened | [NPC][FIRELANDS] Blazing Monstrosity | Confirmed By Tester Dungeon/Raid Later Patch | **Links:**
https://www.wowhead.com/npc=53791/blazing-monstrosity
from WoWHead or our Armory
**What is happening:**
When encounter start they just stand there.
**What should happen:**
These should be mountable and be able to use ablitities
**Is it crashing the server?:**
No
**Other Information:**
... | 1.0 | [NPC][FIRELANDS] Blazing Monstrosity - **Links:**
https://www.wowhead.com/npc=53791/blazing-monstrosity
from WoWHead or our Armory
**What is happening:**
When encounter start they just stand there.
**What should happen:**
These should be mountable and be able to use ablitities
**Is it crashing the server... | non_priority | blazing monstrosity links from wowhead or our armory what is happening when encounter start they just stand there what should happen these should be mountable and be able to use ablitities is it crashing the server no other information | 0 |
32,585 | 4,777,779,475 | IssuesEvent | 2016-10-27 17:15:59 | DynamoRIO/dynamorio | https://api.github.com/repos/DynamoRIO/dynamorio | opened | drcachesim sometimes fails to open pipe file | Bug-Assert Component-DRTool Component-Tests OpSys-Linux | This happened once for a test that passed many many times:
http://dynamorio.org/CDash/testDetails.php?test=141155&build=13692
ASSERT FAILURE: /work/dr/nightly/src/clients/drcachesim/tracer/tracer.cpp:766: fd != -1 ()
| 1.0 | drcachesim sometimes fails to open pipe file - This happened once for a test that passed many many times:
http://dynamorio.org/CDash/testDetails.php?test=141155&build=13692
ASSERT FAILURE: /work/dr/nightly/src/clients/drcachesim/tracer/tracer.cpp:766: fd != -1 ()
| non_priority | drcachesim sometimes fails to open pipe file this happened once for a test that passed many many times assert failure work dr nightly src clients drcachesim tracer tracer cpp fd | 0 |
442,875 | 30,861,448,972 | IssuesEvent | 2023-08-03 03:40:08 | froblesl/git_web_practice_branch | https://api.github.com/repos/froblesl/git_web_practice_branch | opened | Un commit que no sigue la convención de código o arreglo a realizar | documentation | La convención del mensaje del último commit no es la esperada:
`FIX2: Error2`
Recuerde que debe tener el siguiente formato: `<Identificador de la corrección>: <Comentario>`
Para realizar la corrección del mensaje de commit ejecute los comandos `git commit --amend` y `git push -f`
Este issue es solo un recordatorio d... | 1.0 | Un commit que no sigue la convención de código o arreglo a realizar - La convención del mensaje del último commit no es la esperada:
`FIX2: Error2`
Recuerde que debe tener el siguiente formato: `<Identificador de la corrección>: <Comentario>`
Para realizar la corrección del mensaje de commit ejecute los comandos `git... | non_priority | un commit que no sigue la convención de código o arreglo a realizar la convención del mensaje del último commit no es la esperada recuerde que debe tener el siguiente formato para realizar la corrección del mensaje de commit ejecute los comandos git commit amend y git push f este issue es so... | 0 |
58,187 | 8,233,680,374 | IssuesEvent | 2018-09-08 04:09:30 | gatsbyjs/gatsby | https://api.github.com/repos/gatsbyjs/gatsby | closed | Add documentation about service workers | type: documentation | gatsby-plugin-offline adds amazing service worker caching functionality that should be mentioned in the project documentation. | 1.0 | Add documentation about service workers - gatsby-plugin-offline adds amazing service worker caching functionality that should be mentioned in the project documentation. | non_priority | add documentation about service workers gatsby plugin offline adds amazing service worker caching functionality that should be mentioned in the project documentation | 0 |
36,088 | 6,516,011,081 | IssuesEvent | 2017-08-27 00:31:58 | Zimmi48/bugzilla-test | https://api.github.com/repos/Zimmi48/bugzilla-test | closed | firstorder doc variants 2/3 are confused | kind: documentation | Note: the issue was created automatically with bugzilla2github tool
# Bugzilla Bug ID: 4887
Date: 2016-07-02 16:47:34 +0200
From: Jonathan Leivent <<jonikelee@gmail.com>>
To:
CC: coq-bugs-redist@lists.gforge.inria.fr
Last updated: 2016-09-27 17:34:57 +0200
## Bugzilla Comment ID: 12959
Date: 2016-07-02 1... | 1.0 | firstorder doc variants 2/3 are confused - Note: the issue was created automatically with bugzilla2github tool
# Bugzilla Bug ID: 4887
Date: 2016-07-02 16:47:34 +0200
From: Jonathan Leivent <<jonikelee@gmail.com>>
To:
CC: coq-bugs-redist@lists.gforge.inria.fr
Last updated: 2016-09-27 17:34:57 +0200
## Bu... | non_priority | firstorder doc variants are confused note the issue was created automatically with tool bugzilla bug id date from jonathan leivent lt gt to cc coq bugs redist lists gforge inria fr last updated bugzilla comment id date from jonathan le... | 0 |
81,815 | 10,260,843,661 | IssuesEvent | 2019-08-22 08:26:52 | architecture-building-systems/CityEnergyAnalyst | https://api.github.com/repos/architecture-building-systems/CityEnergyAnalyst | closed | Solar radiation documentation correction | documentation | The solar radiation in the dashboard is placed at:
Tools/Energy potentials/Solar radiation (Daysim engine)
But in the documentation it is stated that it can be found at:
tools/Resources/Solar Radiation
| 1.0 | Solar radiation documentation correction - The solar radiation in the dashboard is placed at:
Tools/Energy potentials/Solar radiation (Daysim engine)
But in the documentation it is stated that it can be found at:
tools/Resources/Solar Radiation
| non_priority | solar radiation documentation correction the solar radiation in the dashboard is placed at tools energy potentials solar radiation daysim engine but in the documentation it is stated that it can be found at tools resources solar radiation | 0 |
58,045 | 14,231,037,413 | IssuesEvent | 2020-11-18 09:00:53 | ams0/openhack-containers | https://api.github.com/repos/ams0/openhack-containers | opened | CVE-2019-14893 (High) detected in jackson-databind-2.9.8.jar | security vulnerability | ## CVE-2019-14893 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2019-14893 (High) detected in jackson-databind-2.9.8.jar - ## CVE-2019-14893 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General... | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file openhack containers src user ja... | 0 |
7,931 | 8,124,454,778 | IssuesEvent | 2018-08-16 17:36:39 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Service Fabric Mesh in EU/UK Regions ? | cxp in-progress needs-more-info product-question service-fabric-mesh/svc triaged | Is there any way can I get preview from EU / UK Regions ? or when this will become available as preview in EU / UK Regions ?
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 1772867c-92c7-f8ae-e19a-929478763da3
* Version Independent ID: 2df08... | 1.0 | Service Fabric Mesh in EU/UK Regions ? - Is there any way can I get preview from EU / UK Regions ? or when this will become available as preview in EU / UK Regions ?
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 1772867c-92c7-f8ae-e19a-929... | non_priority | service fabric mesh in eu uk regions is there any way can i get preview from eu uk regions or when this will become available as preview in eu uk regions document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version indepen... | 0 |
19,578 | 4,424,460,379 | IssuesEvent | 2016-08-16 12:39:08 | PerfCake/PerfCake | https://api.github.com/repos/PerfCake/PerfCake | opened | Create standalone execution section in user guide | documentation | Make the information more clear and available. | 1.0 | Create standalone execution section in user guide - Make the information more clear and available. | non_priority | create standalone execution section in user guide make the information more clear and available | 0 |
215,529 | 24,177,217,925 | IssuesEvent | 2022-09-23 04:09:12 | bcgov/CONN-CCBC-portal | https://api.github.com/repos/bcgov/CONN-CCBC-portal | closed | Container Scanning | Blocked inSprint Security | Discuss with Nick Corcoran about container scanning.
This will scan the OS level code that we have imported. | True | Container Scanning - Discuss with Nick Corcoran about container scanning.
This will scan the OS level code that we have imported. | non_priority | container scanning discuss with nick corcoran about container scanning this will scan the os level code that we have imported | 0 |
235,732 | 19,424,876,547 | IssuesEvent | 2021-12-21 03:12:28 | go-gitea/gitea | https://api.github.com/repos/go-gitea/gitea | closed | Integration tests fail if LANG is not "" | kind/bug kind/testing | gitea version: 9296baf
to reproduce:
```
export LANG=de_DE.UTF-8
make test-sqlite
```
expected: they should pass
affected tests:
- TestAPILFSBatch/Download/MetaNotFound (api_repo_lfs_test.go:186 - should be false)
- TestAPILFSUpload/AlreadyExistsInStore (api_repo_lfs_test.go:360 - should be false)
... | 1.0 | Integration tests fail if LANG is not "" - gitea version: 9296baf
to reproduce:
```
export LANG=de_DE.UTF-8
make test-sqlite
```
expected: they should pass
affected tests:
- TestAPILFSBatch/Download/MetaNotFound (api_repo_lfs_test.go:186 - should be false)
- TestAPILFSUpload/AlreadyExistsInStore (api... | non_priority | integration tests fail if lang is not gitea version to reproduce export lang de de utf make test sqlite expected they should pass affected tests testapilfsbatch download metanotfound api repo lfs test go should be false testapilfsupload alreadyexistsinstore api repo lf... | 0 |
130,972 | 18,214,366,228 | IssuesEvent | 2021-09-30 01:02:56 | brogers588/netflix_conductor_fork | https://api.github.com/repos/brogers588/netflix_conductor_fork | opened | CVE-2021-37136 (High) detected in multiple libraries | security vulnerability | ## CVE-2021-37136 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>netty-codec-4.1.41.Final.jar</b>, <b>netty-codec-4.1.27.Final.jar</b>, <b>netty-codec-4.1.32.Final.jar</b>, <b>netty-... | True | CVE-2021-37136 (High) detected in multiple libraries - ## CVE-2021-37136 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>netty-codec-4.1.41.Final.jar</b>, <b>netty-codec-4.1.27.Final.... | non_priority | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries netty codec final jar netty codec final jar netty codec final jar netty codec final jar netty codec final jar netty codec final jar netty is ... | 0 |
100,470 | 8,744,467,747 | IssuesEvent | 2018-12-12 22:21:08 | ampproject/amphtml | https://api.github.com/repos/ampproject/amphtml | closed | Fix broken tests 'should show the body in error test' in `test-errors.js` | P2: Soon Related to: Flaky Tests Type: Bug | This test brakes on multiple browsers in SauceLabs, and was disabled in #19782. Please triage and fix
Disabled test: https://github.com/ampproject/amphtml/pull/19782/files#diff-5bd3d5b9ed366abf44094456feef5f6aR55 | 1.0 | Fix broken tests 'should show the body in error test' in `test-errors.js` - This test brakes on multiple browsers in SauceLabs, and was disabled in #19782. Please triage and fix
Disabled test: https://github.com/ampproject/amphtml/pull/19782/files#diff-5bd3d5b9ed366abf44094456feef5f6aR55 | non_priority | fix broken tests should show the body in error test in test errors js this test brakes on multiple browsers in saucelabs and was disabled in please triage and fix disabled test | 0 |
233,028 | 17,839,636,277 | IssuesEvent | 2021-09-03 08:23:02 | facebookresearch/detectron2 | https://api.github.com/repos/facebookresearch/detectron2 | opened | Multi-Node distributed training with SLURM | documentation | Hi everybody,
I'm wondering how can I run a distributed training on 2 machines from a cluster managed with SLURM?
I read that you have to manually specify the machine rank when you run the `tools/train_net.py` script, but in my case it should be managed by SLURM.
Somebody had the same issue? :smile: | 1.0 | Multi-Node distributed training with SLURM - Hi everybody,
I'm wondering how can I run a distributed training on 2 machines from a cluster managed with SLURM?
I read that you have to manually specify the machine rank when you run the `tools/train_net.py` script, but in my case it should be managed by SLURM.
Somebod... | non_priority | multi node distributed training with slurm hi everybody i m wondering how can i run a distributed training on machines from a cluster managed with slurm i read that you have to manually specify the machine rank when you run the tools train net py script but in my case it should be managed by slurm somebod... | 0 |
5,307 | 3,198,481,697 | IssuesEvent | 2015-10-01 12:31:23 | owncloud/gallery | https://api.github.com/repos/owncloud/gallery | closed | Add images located on external storage if we already have a thumbnail | coder wanted enhancement | This might slow down the initial discovery operation, but it could be possible to check the thumbnails cache to see if we already have the max preview. If we do, we could show the image despite the fact that it's located on external storage.
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it... | 1.0 | Add images located on external storage if we already have a thumbnail - This might slow down the initial discovery operation, but it could be possible to check the thumbnails cache to see if we already have the max preview. If we do, we could show the image despite the fact that it's located on external storage.
<bo... | non_priority | add images located on external storage if we already have a thumbnail this might slow down the initial discovery operation but it could be possible to check the thumbnails cache to see if we already have the max preview if we do we could show the image despite the fact that it s located on external storage ... | 0 |
43,172 | 5,581,534,855 | IssuesEvent | 2017-03-28 19:05:15 | gustafl/youtube-blacklist-chrome-extension | https://api.github.com/repos/gustafl/youtube-blacklist-chrome-extension | opened | Show a live data stream on the web page | design future | Because it's fun and attractive. Ideally, we want to get the images from YouTube too. Websockets is probably the technology I need to learn for this. | 1.0 | Show a live data stream on the web page - Because it's fun and attractive. Ideally, we want to get the images from YouTube too. Websockets is probably the technology I need to learn for this. | non_priority | show a live data stream on the web page because it s fun and attractive ideally we want to get the images from youtube too websockets is probably the technology i need to learn for this | 0 |
98,460 | 12,325,529,452 | IssuesEvent | 2020-05-13 15:10:52 | department-of-veterans-affairs/va.gov-cms | https://api.github.com/repos/department-of-veterans-affairs/va.gov-cms | closed | Iteration on Assignments wireframes, pre-usability testing | Design Research ⭐️ Content ops | ## Description
## Acceptance Criteria
* Wireframe prototype is ready for user testing
| 1.0 | Iteration on Assignments wireframes, pre-usability testing - ## Description
## Acceptance Criteria
* Wireframe prototype is ready for user testing
| non_priority | iteration on assignments wireframes pre usability testing description acceptance criteria wireframe prototype is ready for user testing | 0 |
312,715 | 26,873,909,894 | IssuesEvent | 2023-02-04 20:13:19 | MPMG-DCC-UFMG/F01 | https://api.github.com/repos/MPMG-DCC-UFMG/F01 | closed | Teste de generalizacao para a tag Informações Institucionais - Leis Municipais - Santana do Riacho | generalization test development template - Síntese tecnologia e informatica (88) tag - Informações Institucionais subtag - Leis Municipais | DoD: Realizar o teste de Generalização do validador da tag Informações Institucionais - Leis Municipais para o Município de Santana do Riacho. | 1.0 | Teste de generalizacao para a tag Informações Institucionais - Leis Municipais - Santana do Riacho - DoD: Realizar o teste de Generalização do validador da tag Informações Institucionais - Leis Municipais para o Município de Santana do Riacho. | non_priority | teste de generalizacao para a tag informações institucionais leis municipais santana do riacho dod realizar o teste de generalização do validador da tag informações institucionais leis municipais para o município de santana do riacho | 0 |
47,193 | 10,053,105,797 | IssuesEvent | 2019-07-21 14:08:30 | chungwei/imiao | https://api.github.com/repos/chungwei/imiao | opened | LeetCode-217. 存在重复元素 | LeetCode | 原文链接 [217. 存在重复元素](https://leetcode-cn.com/problems/contains-duplicate/)
```go
func containsDuplicate(nums []int) bool {
m := make(map[int]int)
for _, v := range nums {
if _, ok := m[v]; ok {
return true
}
m[v]++
}
return false
}
``` | 1.0 | LeetCode-217. 存在重复元素 - 原文链接 [217. 存在重复元素](https://leetcode-cn.com/problems/contains-duplicate/)
```go
func containsDuplicate(nums []int) bool {
m := make(map[int]int)
for _, v := range nums {
if _, ok := m[v]; ok {
return true
}
m[v]++
}
return false
}
``` | non_priority | leetcode 存在重复元素 原文链接 go func containsduplicate nums int bool m make map int for v range nums if ok m ok return true m return false | 0 |
262,971 | 27,989,595,348 | IssuesEvent | 2023-03-27 01:45:28 | samq-ghdemo/apache-logging-log4j-kotlin | https://api.github.com/repos/samq-ghdemo/apache-logging-log4j-kotlin | opened | CVE-2020-29582 (Medium) detected in kotlin-stdlib-1.3.72.jar | Mend: dependency security vulnerability | ## CVE-2020-29582 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>kotlin-stdlib-1.3.72.jar</b></p></summary>
<p>Kotlin Standard Library for JVM</p>
<p>Library home page: <a href="htt... | True | CVE-2020-29582 (Medium) detected in kotlin-stdlib-1.3.72.jar - ## CVE-2020-29582 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>kotlin-stdlib-1.3.72.jar</b></p></summary>
<p>Kotlin ... | non_priority | cve medium detected in kotlin stdlib jar cve medium severity vulnerability vulnerable library kotlin stdlib jar kotlin standard library for jvm library home page a href path to dependency file api kotlin pom xml path to vulnerable library tbrains kotlin kotlin st... | 0 |
6,491 | 3,398,444,727 | IssuesEvent | 2015-12-02 03:50:17 | ProjectFacet/facet | https://api.github.com/repos/ProjectFacet/facet | opened | Series | code | A user can view all series of any status that's current. Series are organized by creation date. Meta information about a series should be available in the display or through a modal window or popover.
**View:**
Create a view to return series.
**Template:**
Create a template to display a series. | 1.0 | Series - A user can view all series of any status that's current. Series are organized by creation date. Meta information about a series should be available in the display or through a modal window or popover.
**View:**
Create a view to return series.
**Template:**
Create a template to display a series. | non_priority | series a user can view all series of any status that s current series are organized by creation date meta information about a series should be available in the display or through a modal window or popover view create a view to return series template create a template to display a series | 0 |
167,838 | 20,726,426,016 | IssuesEvent | 2022-03-14 02:51:43 | valdisiljuconoks/FeatureSwitch | https://api.github.com/repos/valdisiljuconoks/FeatureSwitch | opened | CVE-2020-28500 (Medium) detected in lodash-2.4.2.tgz | security vulnerability | ## CVE-2020-28500 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras... | True | CVE-2020-28500 (Medium) detected in lodash-2.4.2.tgz - ## CVE-2020-28500 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library deliv... | non_priority | cve medium detected in lodash tgz cve medium severity vulnerability vulnerable library lodash tgz a utility library delivering consistency customization performance extras library home page a href path to dependency file episample modules protected shell shell ... | 0 |
57,783 | 14,217,865,708 | IssuesEvent | 2020-11-17 10:57:40 | SAP/spartacus | https://api.github.com/repos/SAP/spartacus | closed | Cannot remove coupon if the coupon code is ".." | backend-dependency fellows-friendly security | Cannot remove coupon if the coupon code is ".."
## Environment Details
- Spartacus: development environment
- Browser: Chrome 76.0.3809.132
- OS: macOS Mojave 10.14.6
- Device: macbook
## Steps to Reproduce
1. Create a coupon with code ".."
2. Apply this coupon to a cart
3. Remove this coupon from cart
... | True | Cannot remove coupon if the coupon code is ".." - Cannot remove coupon if the coupon code is ".."
## Environment Details
- Spartacus: development environment
- Browser: Chrome 76.0.3809.132
- OS: macOS Mojave 10.14.6
- Device: macbook
## Steps to Reproduce
1. Create a coupon with code ".."
2. Apply this ... | non_priority | cannot remove coupon if the coupon code is cannot remove coupon if the coupon code is environment details spartacus development environment browser chrome os macos mojave device macbook steps to reproduce create a coupon with code apply this coupon t... | 0 |
326,027 | 24,070,421,896 | IssuesEvent | 2022-09-18 04:32:57 | jupyterlite/demo | https://api.github.com/repos/jupyterlite/demo | closed | pre-install pure python package in static html site | documentation | ### Problem
Not sure if this is possible but I could not figure how to pre-install a pure python package on my jupyterlite static html site.
The example is here:
https://marcocaggioni.github.io/rheolite/lab/index.html
in the notebook the first cell is to micropip install lmfit which works fine but takes some ti... | 1.0 | pre-install pure python package in static html site - ### Problem
Not sure if this is possible but I could not figure how to pre-install a pure python package on my jupyterlite static html site.
The example is here:
https://marcocaggioni.github.io/rheolite/lab/index.html
in the notebook the first cell is to mic... | non_priority | pre install pure python package in static html site problem not sure if this is possible but i could not figure how to pre install a pure python package on my jupyterlite static html site the example is here in the notebook the first cell is to micropip install lmfit which works fine but takes some ti... | 0 |
350,175 | 24,971,792,036 | IssuesEvent | 2022-11-02 02:20:15 | Nuclei-Software/nuclei-linux-sdk | https://api.github.com/repos/Nuclei-Software/nuclei-linux-sdk | opened | opensbi boot traped with a lot of sbi_trap_error | documentation | ## Issue Description and Solution
As image below described:

You can see `mcause = 0x7, mtval = 0x08000000`
mcause check riscv privilege manual is **Store/AMO access f... | 1.0 | opensbi boot traped with a lot of sbi_trap_error - ## Issue Description and Solution
As image below described:

You can see `mcause = 0x7, mtval = 0x08000000`
mcause c... | non_priority | opensbi boot traped with a lot of sbi trap error issue description and solution as image below described you can see mcause mtval mcause check riscv privilege manual is store amo access fault mtval means whether the store access fault happened which is it is the pre... | 0 |
29,281 | 23,875,910,808 | IssuesEvent | 2022-09-07 19:02:10 | accessibility-exchange/platform | https://api.github.com/repos/accessibility-exchange/platform | closed | File does not exist at path /opt/data/storage/framework/views/61cb24237d9772f79862641d9038616e2af923... | help wanted infrastructure | **`Illuminate\Contracts\Filesystem\FileNotFoundException`**
File does not exist at path /opt/data/storage/framework/views/61cb24237d9772f79862641d9038616e2af923b3.php.
:dart: Illuminate\Filesystem\Filesystem::getRequire
:page_facing_up: /app/vendor/laravel/framework/src/Illuminate/Filesystem/Filesystem.php
``... | 1.0 | File does not exist at path /opt/data/storage/framework/views/61cb24237d9772f79862641d9038616e2af923... - **`Illuminate\Contracts\Filesystem\FileNotFoundException`**
File does not exist at path /opt/data/storage/framework/views/61cb24237d9772f79862641d9038616e2af923b3.php.
:dart: Illuminate\Filesystem\Filesystem:... | non_priority | file does not exist at path opt data storage framework views illuminate contracts filesystem filenotfoundexception file does not exist at path opt data storage framework views php dart illuminate filesystem filesystem getrequire page facing up app vendor laravel framework src illuminate f... | 0 |
68,424 | 13,129,893,590 | IssuesEvent | 2020-08-06 14:34:10 | Abbassihraf/P-curiosity-LAB | https://api.github.com/repos/Abbassihraf/P-curiosity-LAB | opened | Popups what we offer section | Code In progress home_page | > ### Desktop
**To Rural Communities**
- [ ] Popup markup
- [ ] Popup styling
- [ ] Popup testing
**To idea-holders**
- [ ] Popup markup
- [ ] Popup styling
- [ ] Popup testing
**To business**
- [ ] Popup markup
- [ ] Popup styling
- [ ] Popup testing
**To researchers & scientifics**
- [ ] Popup... | 1.0 | Popups what we offer section - > ### Desktop
**To Rural Communities**
- [ ] Popup markup
- [ ] Popup styling
- [ ] Popup testing
**To idea-holders**
- [ ] Popup markup
- [ ] Popup styling
- [ ] Popup testing
**To business**
- [ ] Popup markup
- [ ] Popup styling
- [ ] Popup testing
**To researche... | non_priority | popups what we offer section desktop to rural communities popup markup popup styling popup testing to idea holders popup markup popup styling popup testing to business popup markup popup styling popup testing to researchers scientifics ... | 0 |
175,298 | 14,522,809,352 | IssuesEvent | 2020-12-14 09:18:19 | fweik/nrng | https://api.github.com/repos/fweik/nrng | closed | State Goals | documentation | Update the documentation to state what the goals of the library are.
So far planned
1. Range and constrained versions of the stl numerics algorithms
2. Additional numeric algorithms like weighted sums, statistical moments, ...
Maybe
3. Parallel versions
4. Integrations of `std::experimenta::simd`.
Ideas... | 1.0 | State Goals - Update the documentation to state what the goals of the library are.
So far planned
1. Range and constrained versions of the stl numerics algorithms
2. Additional numeric algorithms like weighted sums, statistical moments, ...
Maybe
3. Parallel versions
4. Integrations of `std::experimenta::s... | non_priority | state goals update the documentation to state what the goals of the library are so far planned range and constrained versions of the stl numerics algorithms additional numeric algorithms like weighted sums statistical moments maybe parallel versions integrations of std experimenta s... | 0 |
73,513 | 9,668,962,656 | IssuesEvent | 2019-05-21 16:12:06 | itechub/jane | https://api.github.com/repos/itechub/jane | closed | Add prefix to environment variables | backend documentation refactor | In order to avoid collisions with OS environment variables, rename these variables by adding a `JANE_` prefix.
```
export SECRET_KEY='z1q=7ixu5&o=2lj05uziiemvhi)!z1-d9fwmyo(sqsyzpvg2u_'
export USERNAME='root'
export PASSWORD='123456'
export NAME='jane'
export HOST='localhost'
export PORT=3306
export DEBUG=Tur... | 1.0 | Add prefix to environment variables - In order to avoid collisions with OS environment variables, rename these variables by adding a `JANE_` prefix.
```
export SECRET_KEY='z1q=7ixu5&o=2lj05uziiemvhi)!z1-d9fwmyo(sqsyzpvg2u_'
export USERNAME='root'
export PASSWORD='123456'
export NAME='jane'
export HOST='localhos... | non_priority | add prefix to environment variables in order to avoid collisions with os environment variables rename these variables by adding a jane prefix export secret key o export username root export password export name jane export host localhost export port export debug ture ... | 0 |
334,543 | 24,423,504,963 | IssuesEvent | 2022-10-05 23:05:18 | aws/aws-sdk-java-v2 | https://api.github.com/repos/aws/aws-sdk-java-v2 | closed | "IN" Statement doesn't work with StringSet | service-api documentation service:dynamodb | ## Describe the bug
We are trying to do a query with a `IN` Statement and setting a StringSet in Query Expression
e.g.:
```
--filter-expression 'field1 IN (:fieldList)'
--expression-attribute-values '{":fieldList": {"SS":["value1", "value2"]}}'
```
Documentation isn't clear about this scenario
## Expect... | 1.0 | "IN" Statement doesn't work with StringSet - ## Describe the bug
We are trying to do a query with a `IN` Statement and setting a StringSet in Query Expression
e.g.:
```
--filter-expression 'field1 IN (:fieldList)'
--expression-attribute-values '{":fieldList": {"SS":["value1", "value2"]}}'
```
Documentation... | non_priority | in statement doesn t work with stringset describe the bug we are trying to do a query with a in statement and setting a stringset in query expression e g filter expression in fieldlist expression attribute values fieldlist ss documentation isn t clear about this ... | 0 |
63,712 | 15,707,410,440 | IssuesEvent | 2021-03-26 18:50:27 | tensorflow/tensorflow | https://api.github.com/repos/tensorflow/tensorflow | opened | Please help Conda package tensorflow for OSX | type:build/install | (I get that this is a weird thing to put in an issue)
Right now it's hard for the Anaconda people to make conda packages of Tensorflow for OSX because of gcc-versus-clang issues:
https://github.com/ContinuumIO/anaconda-issues/issues/11697
This is impacting downstream packages that want to use tensorflow, as we ... | 1.0 | Please help Conda package tensorflow for OSX - (I get that this is a weird thing to put in an issue)
Right now it's hard for the Anaconda people to make conda packages of Tensorflow for OSX because of gcc-versus-clang issues:
https://github.com/ContinuumIO/anaconda-issues/issues/11697
This is impacting downstre... | non_priority | please help conda package tensorflow for osx i get that this is a weird thing to put in an issue right now it s hard for the anaconda people to make conda packages of tensorflow for osx because of gcc versus clang issues this is impacting downstream packages that want to use tensorflow as we can t speci... | 0 |
198,278 | 22,621,115,053 | IssuesEvent | 2022-06-30 06:26:51 | ioana-nicolae/keycloak | https://api.github.com/repos/ioana-nicolae/keycloak | opened | CVE-2021-41973 (Medium) detected in mina-core-2.1.3.jar | security vulnerability | ## CVE-2021-41973 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mina-core-2.1.3.jar</b></p></summary>
<p>Apache MINA is a network application framework which helps users develop hi... | True | CVE-2021-41973 (Medium) detected in mina-core-2.1.3.jar - ## CVE-2021-41973 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mina-core-2.1.3.jar</b></p></summary>
<p>Apache MINA is a ... | non_priority | cve medium detected in mina core jar cve medium severity vulnerability vulnerable library mina core jar apache mina is a network application framework which helps users develop high performance and highly scalable network applications easily it provides an abstract event drive... | 0 |
12,026 | 3,250,500,664 | IssuesEvent | 2015-10-19 00:51:23 | photonstorm/phaser | https://api.github.com/repos/photonstorm/phaser | closed | With WebGL, adding child text to button renders text to other buttons | user to test | Creating multiple Phaser.Buttons and giving them Phaser.Text children will result in both the buttons and children to be rendered and subsequent labels to be rendered on previously created buttons.
This problem is only reproducible when using WebGL (and not Canvas) as Phaser's renderer.
This bug is seen as a regr... | 1.0 | With WebGL, adding child text to button renders text to other buttons - Creating multiple Phaser.Buttons and giving them Phaser.Text children will result in both the buttons and children to be rendered and subsequent labels to be rendered on previously created buttons.
This problem is only reproducible when using We... | non_priority | with webgl adding child text to button renders text to other buttons creating multiple phaser buttons and giving them phaser text children will result in both the buttons and children to be rendered and subsequent labels to be rendered on previously created buttons this problem is only reproducible when using we... | 0 |
387,415 | 26,722,807,189 | IssuesEvent | 2023-01-29 10:51:01 | PerimeterX/marshmallow | https://api.github.com/repos/PerimeterX/marshmallow | closed | Is there a way to marshal de JSON | documentation | Hi!
I am looking for a way to read, modify and save a JSON of which I am only interested in part of its content.
This package looks like it could be useful for the first two steps, but I'm not sure about the last one.
Is there any way to do it? Either through the API of the package or in some recommended way.
T... | 1.0 | Is there a way to marshal de JSON - Hi!
I am looking for a way to read, modify and save a JSON of which I am only interested in part of its content.
This package looks like it could be useful for the first two steps, but I'm not sure about the last one.
Is there any way to do it? Either through the API of the pack... | non_priority | is there a way to marshal de json hi i am looking for a way to read modify and save a json of which i am only interested in part of its content this package looks like it could be useful for the first two steps but i m not sure about the last one is there any way to do it either through the api of the pack... | 0 |
74,598 | 20,250,091,212 | IssuesEvent | 2022-02-14 17:03:00 | bottlerocket-os/bottlerocket-test-system | https://api.github.com/repos/bottlerocket-os/bottlerocket-test-system | closed | certificates missing in agents | bug resource-agent test-agent build |
```
kubectl logs x86-64-aws-k8s-121-creation-s2h8k
[2022-02-14T01:30:43Z INFO eks_resource_agent::eks_provider] Beginning creation of EKS cluster 'x86-64-aws-k8s-121' with creation policy 'Some(IfNotExists)'
thread 'main' panicked at 'no CA certificates found', /src/.cargo/registry/src/github.com-1ecc6299db9ec823... | 1.0 | certificates missing in agents -
```
kubectl logs x86-64-aws-k8s-121-creation-s2h8k
[2022-02-14T01:30:43Z INFO eks_resource_agent::eks_provider] Beginning creation of EKS cluster 'x86-64-aws-k8s-121' with creation policy 'Some(IfNotExists)'
thread 'main' panicked at 'no CA certificates found', /src/.cargo/registr... | non_priority | certificates missing in agents kubectl logs aws creation beginning creation of eks cluster aws with creation policy some ifnotexists thread main panicked at no ca certificates found src cargo registry src github com hyper rustls src connector rs note run with ru... | 0 |
84,919 | 10,421,311,023 | IssuesEvent | 2019-09-16 05:35:37 | trevorld/r-optparse | https://api.github.com/repos/trevorld/r-optparse | closed | Throw error if short flag more than one character long | documentation | Hello,
The opt list contains different values while executing a script by command-line (Rscript) versus RStudio. Here's the code:
```
#!/usr/bin/env Rscript
suppressMessages(library('optparse'))
options(show.error.locations = TRUE)
#### ARGUMENTS ####
option_list = list(
make_option(c("-i","--... | 1.0 | Throw error if short flag more than one character long - Hello,
The opt list contains different values while executing a script by command-line (Rscript) versus RStudio. Here's the code:
```
#!/usr/bin/env Rscript
suppressMessages(library('optparse'))
options(show.error.locations = TRUE)
#### ARGUMENTS ... | non_priority | throw error if short flag more than one character long hello the opt list contains different values while executing a script by command line rscript versus rstudio here s the code usr bin env rscript suppressmessages library optparse options show error locations true arguments ... | 0 |
69,166 | 14,973,457,354 | IssuesEvent | 2021-01-28 01:07:34 | TreyM-WSS/catalog-profiler-examples | https://api.github.com/repos/TreyM-WSS/catalog-profiler-examples | opened | CVE-2020-35490 (High) detected in jackson-databind-2.9.8.jar | security vulnerability | ## CVE-2020-35490 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2020-35490 (High) detected in jackson-databind-2.9.8.jar - ## CVE-2020-35490 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General... | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file catalog profiler examples build... | 0 |
83,170 | 10,329,221,959 | IssuesEvent | 2019-09-02 11:37:22 | mhmdtshref/portfolio | https://api.github.com/repos/mhmdtshref/portfolio | closed | Create language page component | design feature technical | Using Figma design, create the service page component which gets services from the backend. | 1.0 | Create language page component - Using Figma design, create the service page component which gets services from the backend. | non_priority | create language page component using figma design create the service page component which gets services from the backend | 0 |
2,814 | 12,641,414,202 | IssuesEvent | 2020-06-16 06:05:55 | Shirataki2/WebBash | https://api.github.com/repos/Shirataki2/WebBash | closed | Test on Predeployでの条件変更とRelease Drafterの微修正 | Automation Chore | `.github/release-drafter.yml`
```yml
name-template: "v$NEXT_PATCH_VERSION"
tag-template: "v$NEXT_PATCH_VERSION"
categories:
- title: "🚀 新機能"
labels:
- "Feature"
- title: "🐛 バグ修正"
labels:
- "Bug"
- title: "🧰 メンテナンス"
labels:
- "chore" <- 大文字にする
- title: "🤖 自動化"
... | 1.0 | Test on Predeployでの条件変更とRelease Drafterの微修正 - `.github/release-drafter.yml`
```yml
name-template: "v$NEXT_PATCH_VERSION"
tag-template: "v$NEXT_PATCH_VERSION"
categories:
- title: "🚀 新機能"
labels:
- "Feature"
- title: "🐛 バグ修正"
labels:
- "Bug"
- title: "🧰 メンテナンス"
labels:
... | non_priority | test on predeployでの条件変更とrelease drafterの微修正 github release drafter yml yml name template v next patch version tag template v next patch version categories title 🚀 新機能 labels feature title 🐛 バグ修正 labels bug title 🧰 メンテナンス labels ... | 0 |
41,290 | 6,899,094,556 | IssuesEvent | 2017-11-24 12:16:24 | bio2bel/ec | https://api.github.com/repos/bio2bel/ec | closed | Fill out all rtype in manager | documentation | It's a lot of the time more informative to have the `:rtype:` filled out in the documentation because then PyCharm can introspect and give better suggestions | 1.0 | Fill out all rtype in manager - It's a lot of the time more informative to have the `:rtype:` filled out in the documentation because then PyCharm can introspect and give better suggestions | non_priority | fill out all rtype in manager it s a lot of the time more informative to have the rtype filled out in the documentation because then pycharm can introspect and give better suggestions | 0 |
137,986 | 11,171,920,734 | IssuesEvent | 2019-12-29 00:23:51 | HRSEVESOSK/cide-ionic-app | https://api.github.com/repos/HRSEVESOSK/cide-ionic-app | opened | Correct names of Institutions | testing | Name of institutions should be in Croatian. The name of institution for ICZ/Inspekcije civilne zaštite” is missing and should be: „Ministsrstvo unutarnjih poslova Ravnateljstvo civilne zaštite“.

Note 14... | 1.0 | Correct names of Institutions - Name of institutions should be in Croatian. The name of institution for ICZ/Inspekcije civilne zaštite” is missing and should be: „Ministsrstvo unutarnjih poslova Ravnateljstvo civilne zaštite“.
 detected in linux-yoctov5.4.51 - autoclosed | security vulnerability | ## CVE-2018-20669 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.... | True | CVE-2018-20669 (High) detected in linux-yoctov5.4.51 - autoclosed - ## CVE-2018-20669 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto ... | non_priority | cve high detected in linux autoclosed cve high severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in head commit a href found in base branch master vulnerable source files ... | 0 |
27,705 | 4,326,601,532 | IssuesEvent | 2016-07-26 07:14:20 | QualiSystems/AWS-Shell | https://api.github.com/repos/QualiSystems/AWS-Shell | closed | Delete Instance command | Blocked by Bug F-deployment Test Plan Version 7.1 | Terminate the AWS instance only
this command should be hidden and will be called by RemoveResourceFromReservation
we should delete all entities related to this instance as part of this command.
For now only delete the exclusive Security Group.
The deletion of storage will be handled in another story.
**there will be... | 1.0 | Delete Instance command - Terminate the AWS instance only
this command should be hidden and will be called by RemoveResourceFromReservation
we should delete all entities related to this instance as part of this command.
For now only delete the exclusive Security Group.
The deletion of storage will be handled in anoth... | non_priority | delete instance command terminate the aws instance only this command should be hidden and will be called by removeresourcefromreservation we should delete all entities related to this instance as part of this command for now only delete the exclusive security group the deletion of storage will be handled in anoth... | 0 |
4,740 | 2,871,982,018 | IssuesEvent | 2015-06-08 08:51:33 | dotse/zonemaster-backend | https://api.github.com/repos/dotse/zonemaster-backend | closed | Method #5 (start_domain_test) cant be run using API.md | documentation Prio High | This document (https://github.com/dotse/zonemaster-backend/blob/master/docs/API.md) needs to have functioning examples (that are always updated if the API changes). When I try to run method "start_domain_test" it returns:
{"error":{"message":"Failed to parse json","code":-32700}}
Please add a working example to ... | 1.0 | Method #5 (start_domain_test) cant be run using API.md - This document (https://github.com/dotse/zonemaster-backend/blob/master/docs/API.md) needs to have functioning examples (that are always updated if the API changes). When I try to run method "start_domain_test" it returns:
{"error":{"message":"Failed to parse j... | non_priority | method start domain test cant be run using api md this document needs to have functioning examples that are always updated if the api changes when i try to run method start domain test it returns error message failed to parse json code please add a working example to the document ... | 0 |
5,473 | 12,543,953,875 | IssuesEvent | 2020-06-05 16:24:39 | MicrosoftDocs/architecture-center | https://api.github.com/repos/MicrosoftDocs/architecture-center | closed | Typo in Reference Architecture | Pri1 architecture-center/svc assigned-to-author cxp doc-enhancement solution-idea/subsvc triaged | In the reference architecture diagram for the first step it mentions as Azure Data Lake Storage but in the Data Flow step 1 it mentions as Azure Blob Storage.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 1b68d40f-4b98-396b-f4c3-b8... | 1.0 | Typo in Reference Architecture - In the reference architecture diagram for the first step it mentions as Azure Data Lake Storage but in the Data Flow step 1 it mentions as Azure Blob Storage.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
... | non_priority | typo in reference architecture in the reference architecture diagram for the first step it mentions as azure data lake storage but in the data flow step it mentions as azure blob storage document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking ... | 0 |
50,645 | 21,263,150,651 | IssuesEvent | 2022-04-13 07:20:24 | BlackstarDigitalTeam/KetteringReleases | https://api.github.com/repos/BlackstarDigitalTeam/KetteringReleases | closed | [Architect v1.1.2] - Error Connecting | Customer Service | Architect: v1.1.2
OS: Windows 10
Device Model: Not connected
Device Version:
Description:I have a connection problem with my amp it is on and it is connected to the both devices. You can even hear the computer sounds through the amp but yet still the software does not recognize my amp. | 1.0 | [Architect v1.1.2] - Error Connecting - Architect: v1.1.2
OS: Windows 10
Device Model: Not connected
Device Version:
Description:I have a connection problem with my amp it is on and it is connected to the both devices. You can even hear the computer sounds through the amp but yet still the software does not recognize ... | non_priority | error connecting architect os windows device model not connected device version description i have a connection problem with my amp it is on and it is connected to the both devices you can even hear the computer sounds through the amp but yet still the software does not recognize my amp | 0 |
217,616 | 16,723,146,622 | IssuesEvent | 2021-06-10 09:43:35 | djfoster21/mcDuckBroker | https://api.github.com/repos/djfoster21/mcDuckBroker | opened | Webs para ver volumen y liquidaciones de un activo (pools de liquidez) (Futuros) | documentation | https://www.paguertrading.com/pools/
https://btcusd.aggr.trade/#
El precio va a tender a llegar a donde se encuentran la mayor cantidad de liquidaciones.
Esto sirve más que nada para abrir posiciones en futuros, aunque también se podría usar para spot.
| 1.0 | Webs para ver volumen y liquidaciones de un activo (pools de liquidez) (Futuros) - https://www.paguertrading.com/pools/
https://btcusd.aggr.trade/#
El precio va a tender a llegar a donde se encuentran la mayor cantidad de liquidaciones.
Esto sirve más que nada para abrir posiciones en futuros, aunque también s... | non_priority | webs para ver volumen y liquidaciones de un activo pools de liquidez futuros el precio va a tender a llegar a donde se encuentran la mayor cantidad de liquidaciones esto sirve más que nada para abrir posiciones en futuros aunque también se podría usar para spot | 0 |
7,464 | 6,965,245,703 | IssuesEvent | 2017-12-09 03:35:24 | nyu-devops-customers/customers | https://api.github.com/repos/nyu-devops-customers/customers | closed | MySQL data backup mechanism | infrastructure performance | **As a** developer
**I need** to backup users' data
**So that** to avoid unexpected data loss
**Assumptions:**
* Use a static SQL file as a backup
**Acceptance Criteria:**
When I backup my database
Then I delete my original tables and restore it with my backup file
I can get all my data back
| 1.0 | MySQL data backup mechanism - **As a** developer
**I need** to backup users' data
**So that** to avoid unexpected data loss
**Assumptions:**
* Use a static SQL file as a backup
**Acceptance Criteria:**
When I backup my database
Then I delete my original tables and restore it with my backup file
I can get a... | non_priority | mysql data backup mechanism as a developer i need to backup users data so that to avoid unexpected data loss assumptions use a static sql file as a backup acceptance criteria when i backup my database then i delete my original tables and restore it with my backup file i can get a... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.