Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12
values | text_combine stringlengths 96 261k | label stringclasses 2
values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
25,218 | 5,143,754,521 | IssuesEvent | 2017-01-12 16:46:00 | socketio/socket.io | https://api.github.com/repos/socketio/socket.io | closed | Please provide propper browser support documentation | Closed due to inactivity Documentation | Please provide documentation on which browsers/versions are supported. "Works on every device" does not inspire production use. A simple table will suffice.
| 1.0 | Please provide propper browser support documentation - Please provide documentation on which browsers/versions are supported. "Works on every device" does not inspire production use. A simple table will suffice.
| non_priority | please provide propper browser support documentation please provide documentation on which browsers versions are supported works on every device does not inspire production use a simple table will suffice | 0 |
2,757 | 12,541,183,540 | IssuesEvent | 2020-06-05 11:50:58 | input-output-hk/cardano-node | https://api.github.com/repos/input-output-hk/cardano-node | opened | [QA] - Create complex transactions | e2e automation | - 1 input, 5 outputs
- 15 inputs, 35 outputs
- 100 inputs, 200 outputs !? | 1.0 | [QA] - Create complex transactions - - 1 input, 5 outputs
- 15 inputs, 35 outputs
- 100 inputs, 200 outputs !? | non_priority | create complex transactions input outputs inputs outputs inputs outputs | 0 |
114,311 | 9,695,675,411 | IssuesEvent | 2019-05-24 23:54:49 | microsoft/vscode | https://api.github.com/repos/microsoft/vscode | opened | Test extract type refactoring for TypeScript | testplan-item | Test for #74243
- [ ] any
- [ ] any
Complexity: 1
**Overview**
TypeScript includes a new refactoring: extract type. This takes a selected type and extracts it to a type alias
Test this new refactoring. Can you extract what you expect? Are there any bugs with the extraction? | 1.0 | Test extract type refactoring for TypeScript - Test for #74243
- [ ] any
- [ ] any
Complexity: 1
**Overview**
TypeScript includes a new refactoring: extract type. This takes a selected type and extracts it to a type alias
Test this new refactoring. Can you extract what you expect? Are there any bugs with... | non_priority | test extract type refactoring for typescript test for any any complexity overview typescript includes a new refactoring extract type this takes a selected type and extracts it to a type alias test this new refactoring can you extract what you expect are there any bugs with the ext... | 0 |
156,448 | 24,623,910,303 | IssuesEvent | 2022-10-16 09:03:54 | dotnet/efcore | https://api.github.com/repos/dotnet/efcore | closed | Use update pipeline to get DML commands for HistoryRepository | closed-by-design | While implementing the `HistoryRepository`, I was trying to get simple `INSERT` and `DELETE` statements out of the Update pipeline. I traced it back to having to create `InternalEntityEntry` object, but that was impractical due to all its dependencies. We should look at simplifying this scenario.
Also, I needed the ab... | 1.0 | Use update pipeline to get DML commands for HistoryRepository - While implementing the `HistoryRepository`, I was trying to get simple `INSERT` and `DELETE` statements out of the Update pipeline. I traced it back to having to create `InternalEntityEntry` object, but that was impractical due to all its dependencies. We ... | non_priority | use update pipeline to get dml commands for historyrepository while implementing the historyrepository i was trying to get simple insert and delete statements out of the update pipeline i traced it back to having to create internalentityentry object but that was impractical due to all its dependencies we ... | 0 |
206,492 | 16,043,900,133 | IssuesEvent | 2021-04-22 11:22:27 | V-A-collaboration/v-en-a | https://api.github.com/repos/V-A-collaboration/v-en-a | closed | Documentatie in Docs folder niet meer up to date | documentation | De website in de docs folder die voor de Github pages wordt gebruikt is niet meer up to date.
De Readme in the repository is accurater.
Het idee is om de tekst in de readme van repository naar de Wiki te verplaatsen en daar verder te update & aan te vullen.
Huidige readme in de repository kan dan gebruikt worden van... | 1.0 | Documentatie in Docs folder niet meer up to date - De website in de docs folder die voor de Github pages wordt gebruikt is niet meer up to date.
De Readme in the repository is accurater.
Het idee is om de tekst in de readme van repository naar de Wiki te verplaatsen en daar verder te update & aan te vullen.
Huidige ... | non_priority | documentatie in docs folder niet meer up to date de website in de docs folder die voor de github pages wordt gebruikt is niet meer up to date de readme in the repository is accurater het idee is om de tekst in de readme van repository naar de wiki te verplaatsen en daar verder te update aan te vullen huidige ... | 0 |
424,908 | 29,183,543,046 | IssuesEvent | 2023-05-19 13:45:58 | kubecub/go-project-layout | https://api.github.com/repos/kubecub/go-project-layout | closed | Bug reports for links in kubecub docs | kind/documentation triage/unresolved report | ## Summary
| Status | Count |
|---------------|-------|
| 🔍 Total | 148 |
| ✅ Successful | 146 |
| ⏳ Timeouts | 1 |
| 🔀 Redirected | 0 |
| 👻 Excluded | 0 |
| ❓ Unknown | 0 |
| 🚫 Errors | 1 |
## Errors per input
### Errors in README.md
* [400] [https://github.com/is... | 1.0 | Bug reports for links in kubecub docs - ## Summary
| Status | Count |
|---------------|-------|
| 🔍 Total | 148 |
| ✅ Successful | 146 |
| ⏳ Timeouts | 1 |
| 🔀 Redirected | 0 |
| 👻 Excluded | 0 |
| ❓ Unknown | 0 |
| 🚫 Errors | 1 |
## Errors per input
### Errors in R... | non_priority | bug reports for links in kubecub docs summary status count 🔍 total ✅ successful ⏳ timeouts 🔀 redirected 👻 excluded ❓ unknown 🚫 errors errors per input errors in readm... | 0 |
63,995 | 12,406,818,852 | IssuesEvent | 2020-05-21 19:51:52 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | Vector64 and Vector128.Create doesn't generate movi for long immediates | area-CodeGen-coreclr | `Vector64.Create` and `Vector128.Create` don't generate `movi` as the other types do for immediate inputs. This appears to be because the logic is using `IsCnsIntOrI` whioch will miss `GT_CNS_LNG`: https://github.com/dotnet/runtime/blob/master/src/coreclr/src/jit/lowerarmarch.cpp#L933-L957
CC. @kunalspathak, @CarolE... | 1.0 | Vector64 and Vector128.Create doesn't generate movi for long immediates - `Vector64.Create` and `Vector128.Create` don't generate `movi` as the other types do for immediate inputs. This appears to be because the logic is using `IsCnsIntOrI` whioch will miss `GT_CNS_LNG`: https://github.com/dotnet/runtime/blob/master/sr... | non_priority | and create doesn t generate movi for long immediates create and create don t generate movi as the other types do for immediate inputs this appears to be because the logic is using iscnsintori whioch will miss gt cns lng cc kunalspathak caroleidt echesakovmsft | 0 |
182,484 | 21,664,527,591 | IssuesEvent | 2022-05-07 01:39:26 | tt9133github/ForTest2 | https://api.github.com/repos/tt9133github/ForTest2 | closed | CVE-2014-2054 (High) detected in moodle/moodle-v2.6.2 - autoclosed | security vulnerability | ## CVE-2014-2054 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>moodle/moodle-v2.6.2</b></p></summary>
<p>Moodle - the world's open source learning platform</p>
<p>
Dependency Hierar... | True | CVE-2014-2054 (High) detected in moodle/moodle-v2.6.2 - autoclosed - ## CVE-2014-2054 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>moodle/moodle-v2.6.2</b></p></summary>
<p>Moodle -... | non_priority | cve high detected in moodle moodle autoclosed cve high severity vulnerability vulnerable library moodle moodle moodle the world s open source learning platform dependency hierarchy x moodle moodle vulnerable library found in head commit a href ... | 0 |
92,684 | 18,922,206,636 | IssuesEvent | 2021-11-17 04:02:11 | libai8723/front-end-dev-notes-bignerdbook | https://api.github.com/repos/libai8723/front-end-dev-notes-bignerdbook | closed | LeetCode 62. Unique Paths | DP LeetCode | https://leetcode.com/problems/unique-paths/
非常简单和典型的一个DP题目,使用 dp[i][j] 来表示从[1,1]到[i,j]的独立唯一的路径数量。
那么 dp[i][j] = dp[i-1][j] + dp[i][j-1];
总体来看比较简单:
```java
public int uniquePaths(int m, int n) {
int[][] dp = new int[m+1][n+1];
for (int i = 0; i < dp.length; i++) {
dp[i][1] = ... | 1.0 | LeetCode 62. Unique Paths - https://leetcode.com/problems/unique-paths/
非常简单和典型的一个DP题目,使用 dp[i][j] 来表示从[1,1]到[i,j]的独立唯一的路径数量。
那么 dp[i][j] = dp[i-1][j] + dp[i][j-1];
总体来看比较简单:
```java
public int uniquePaths(int m, int n) {
int[][] dp = new int[m+1][n+1];
for (int i = 0; i < dp.length; i++... | non_priority | leetcode unique paths 非常简单和典型的一个dp题目,使用 dp 来表示从 到 的独立唯一的路径数量。 那么 dp dp dp 总体来看比较简单: java public int uniquepaths int m int n int dp new int for int i i dp length i dp for int i i dp length i ... | 0 |
246,146 | 18,837,382,236 | IssuesEvent | 2021-11-11 03:47:46 | shahabyazdi/react-multi-date-picker | https://api.github.com/repos/shahabyazdi/react-multi-date-picker | closed | How to prevent calendar marking event? | documentation | I intend to do a recurrence check when marking a date in the multiple calendar, but the onChange event always returns the array with the clicked date already contained and always marks it in the calendar before the setState in its value=[]
Even being a controlled component, values seem to be ignored by the calenda... | 1.0 | How to prevent calendar marking event? - I intend to do a recurrence check when marking a date in the multiple calendar, but the onChange event always returns the array with the clicked date already contained and always marks it in the calendar before the setState in its value=[]
Even being a controlled component, v... | non_priority | how to prevent calendar marking event i intend to do a recurrence check when marking a date in the multiple calendar but the onchange event always returns the array with the clicked date already contained and always marks it in the calendar before the setstate in its value even being a controlled component va... | 0 |
21,833 | 3,924,132,181 | IssuesEvent | 2016-04-22 14:13:40 | tomchadwin/qgis2web | https://api.github.com/repos/tomchadwin/qgis2web | closed | Many more unit tests needed | tests | The tests currently include:
- single layer
- Leaflet or OL3
- point, line, or polygon
- single, categorized, or graduated
- JSON or WMS (WMS only in Leaflet)
Other than that, all options, both per-layer and general, are left with their default values. This means that many things are not tested.
### Per-laye... | 1.0 | Many more unit tests needed - The tests currently include:
- single layer
- Leaflet or OL3
- point, line, or polygon
- single, categorized, or graduated
- JSON or WMS (WMS only in Leaflet)
Other than that, all options, both per-layer and general, are left with their default values. This means that many things a... | non_priority | many more unit tests needed the tests currently include single layer leaflet or point line or polygon single categorized or graduated json or wms wms only in leaflet other than that all options both per layer and general are left with their default values this means that many things are... | 0 |
20,309 | 3,576,049,901 | IssuesEvent | 2016-01-27 18:03:11 | NAFITH/IraqWeb | https://api.github.com/repos/NAFITH/IraqWeb | opened | In LCL Cargo release page, switch the mode to view mode after saving | Cargo Release LCL Major Missing System Design Open |
Berth Operator
Cargo release –Add LCL
Prerequisite:
• Bill of lading of type containers
• Containers loaded to a berth
The container is not connected to a waybill
Scenario
• Log into the system
• From the main menu, click on cargo release
• From the cargo release, click on add CLC
... | 1.0 | In LCL Cargo release page, switch the mode to view mode after saving -
Berth Operator
Cargo release –Add LCL
Prerequisite:
• Bill of lading of type containers
• Containers loaded to a berth
The container is not connected to a waybill
Scenario
• Log into the system
• From the main m... | non_priority | in lcl cargo release page switch the mode to view mode after saving berth operator cargo release –add lcl prerequisite • bill of lading of type containers • containers loaded to a berth the container is not connected to a waybill scenario • log into the system • from the main m... | 0 |
92,111 | 18,770,899,790 | IssuesEvent | 2021-11-06 20:25:08 | nim-lang/Nim | https://api.github.com/repos/nim-lang/Nim | closed | Strange compiler output for parallel/spawn | Codegen Semcheck Threads | ```nim
# nim c --threads:on t2.nim
import threadpool
{.experimental.}
proc xsort(d: var openArray[int]; s: int) =
if s == 0:
swap(d[0], d[1])
else:
swap(d[2], d[3])
proc main =
var d = @[1, 0, 3, 2]
parallel:
spawn xsort(d, 0)
spawn xsort(d, 1)
echo d
main()
```
```
... | 1.0 | Strange compiler output for parallel/spawn - ```nim
# nim c --threads:on t2.nim
import threadpool
{.experimental.}
proc xsort(d: var openArray[int]; s: int) =
if s == 0:
swap(d[0], d[1])
else:
swap(d[2], d[3])
proc main =
var d = @[1, 0, 3, 2]
parallel:
spawn xsort(d, 0)
spawn x... | non_priority | strange compiler output for parallel spawn nim nim c threads on nim import threadpool experimental proc xsort d var openarray s int if s swap d d else swap d d proc main var d parallel spawn xsort d spawn xsort d echo d ... | 0 |
36,913 | 12,429,015,241 | IssuesEvent | 2020-05-25 07:37:16 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | closed | Replace Bazaar with Breezy | 1.severity: security 6.topic: python | **Issue description**
[Bazaar](http://wiki.bazaar.canonical.com/Download) is in maintenance mode and stuck at python 2.7, which is now officially unsupported.
A fork called [Breezy](https://www.breezy-vcs.org/), which is backward compatible and supports python 3, has been available for a while and should replace it.
... | True | Replace Bazaar with Breezy - **Issue description**
[Bazaar](http://wiki.bazaar.canonical.com/Download) is in maintenance mode and stuck at python 2.7, which is now officially unsupported.
A fork called [Breezy](https://www.breezy-vcs.org/), which is backward compatible and supports python 3, has been available for a ... | non_priority | replace bazaar with breezy issue description is in maintenance mode and stuck at python which is now officially unsupported a fork called which is backward compatible and supports python has been available for a while and should replace it possible course of action package breezy ... | 0 |
103,832 | 16,610,437,124 | IssuesEvent | 2021-06-02 10:47:57 | Thanraj/OpenSSL_ | https://api.github.com/repos/Thanraj/OpenSSL_ | opened | CVE-2016-2178 (Medium) detected in opensslOpenSSL_1_0_2 | security vulnerability | ## CVE-2016-2178 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opensslOpenSSL_1_0_2</b></p></summary>
<p>
<p>TLS/SSL and crypto library</p>
<p>Library home page: <a href=https://gi... | True | CVE-2016-2178 (Medium) detected in opensslOpenSSL_1_0_2 - ## CVE-2016-2178 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opensslOpenSSL_1_0_2</b></p></summary>
<p>
<p>TLS/SSL and c... | non_priority | cve medium detected in opensslopenssl cve medium severity vulnerability vulnerable library opensslopenssl tls ssl and crypto library library home page a href found in head commit a href found in base branch master vulnerable source files ... | 0 |
262,071 | 22,793,025,277 | IssuesEvent | 2022-07-10 09:41:41 | void-linux/void-packages | https://api.github.com/repos/void-linux/void-packages | closed | Gnome-shell high cpu usage together with ibus-daemon | bug needs-testing | ### Is this a new report?
Yes
### System Info
Void 5.18.9_1 x86_64 AuthenticAMD uptodate FFF
### Package(s) Affected
gnome-shell-42.3_2
### Does a report exist for this bug with the project's home (upstream) and/or another distro?
https://gitlab.gnome.org/GNOME/gnome-shell/-/raw/gnome-42/NEWS
http... | 1.0 | Gnome-shell high cpu usage together with ibus-daemon - ### Is this a new report?
Yes
### System Info
Void 5.18.9_1 x86_64 AuthenticAMD uptodate FFF
### Package(s) Affected
gnome-shell-42.3_2
### Does a report exist for this bug with the project's home (upstream) and/or another distro?
https://gitla... | non_priority | gnome shell high cpu usage together with ibus daemon is this a new report yes system info void authenticamd uptodate fff package s affected gnome shell does a report exist for this bug with the project s home upstream and or another distro i believe ... | 0 |
256,002 | 22,013,212,170 | IssuesEvent | 2022-05-27 00:48:15 | YawLighthouse/UMG-Slate-Compendium | https://api.github.com/repos/YawLighthouse/UMG-Slate-Compendium | closed | [BUG] Images not showing up properly on certain GitHub themes | Bug InProgress NeedsTesting | GitHub light theme isn't showing some images properly but in other themes they show up just fine. | 1.0 | [BUG] Images not showing up properly on certain GitHub themes - GitHub light theme isn't showing some images properly but in other themes they show up just fine. | non_priority | images not showing up properly on certain github themes github light theme isn t showing some images properly but in other themes they show up just fine | 0 |
76,480 | 21,466,804,577 | IssuesEvent | 2022-04-26 05:13:50 | Drake53/War3Net | https://api.github.com/repos/Drake53/War3Net | closed | Throwing warnings on "item with same key" instead of exception | Area-Build Area-CodeAnalysis | I'm getting the following error when I try to build my map. This only happens to the Azeroth Wars map; it doesn't occur if I do the same operation on another source .w3x.
I don't doubt that the error is correct; my map data is probably broken in some respect. But I also don't have any way to fix that data, so I wond... | 1.0 | Throwing warnings on "item with same key" instead of exception - I'm getting the following error when I try to build my map. This only happens to the Azeroth Wars map; it doesn't occur if I do the same operation on another source .w3x.
I don't doubt that the error is correct; my map data is probably broken in some r... | non_priority | throwing warnings on item with same key instead of exception i m getting the following error when i try to build my map this only happens to the azeroth wars map it doesn t occur if i do the same operation on another source i don t doubt that the error is correct my map data is probably broken in some res... | 0 |
263,108 | 23,036,617,599 | IssuesEvent | 2022-07-22 19:34:16 | OvercastCommunity/public-competitive | https://api.github.com/repos/OvercastCommunity/public-competitive | closed | [CTF/5v5] Remnant | contest | ### Checklist
Check what applies to you. *Add an X between the brackets or click the checkboxes when you have submitted the issue.*
- [X] I have [pruned](https://pgm.dev/docs/guides/packaging/pruning-chunks) the map
- [X] I have agreed with assigning the [CC BY-SA 4.0 license](https://creativecommons.org/licenses/by... | 1.0 | [CTF/5v5] Remnant - ### Checklist
Check what applies to you. *Add an X between the brackets or click the checkboxes when you have submitted the issue.*
- [X] I have [pruned](https://pgm.dev/docs/guides/packaging/pruning-chunks) the map
- [X] I have agreed with assigning the [CC BY-SA 4.0 license](https://creativecom... | non_priority | remnant checklist check what applies to you add an x between the brackets or click the checkboxes when you have submitted the issue i have the map i have agreed with assigning the to this map i have provided an xml file i have uploaded the map zip file to a file sharing service ... | 0 |
241,425 | 26,256,783,758 | IssuesEvent | 2023-01-06 01:57:34 | Chiencc/Express | https://api.github.com/repos/Chiencc/Express | closed | CVE-2021-35065 (High) detected in glob-parent-5.1.2.tgz - autoclosed | security vulnerability | ## CVE-2021-35065 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>glob-parent-5.1.2.tgz</b></p></summary>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home p... | True | CVE-2021-35065 (High) detected in glob-parent-5.1.2.tgz - autoclosed - ## CVE-2021-35065 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>glob-parent-5.1.2.tgz</b></p></summary>
<p>Extr... | non_priority | cve high detected in glob parent tgz autoclosed cve high severity vulnerability vulnerable library glob parent tgz extract the non magic parent path from a glob string library home page a href path to dependency file package json path to vulnerable library node ... | 0 |
5,876 | 3,688,381,419 | IssuesEvent | 2016-02-25 12:38:31 | OpenRCT2/OpenRCT2 | https://api.github.com/repos/OpenRCT2/OpenRCT2 | closed | Crash by segmentation fault 11 on OS X | build OS X (OS) | **OS:** OS X 10.11.3 (15D21)
**Version:** 0.0.4
**Commit:** 10dbcfe, current latest develop
Explanation of the issue...
- [ ] ?
**Steps to reproduce:**
1. Build.
2. Run.
3. …
4. ~~PROFIT!~~
**Screenshot:**

**Version:** 0.0.4
**Commit:** 10dbcfe, current latest develop
Explanation of the issue...
- [ ] ?
**Steps to reproduce:**
1. Build.
2. Run.
3. …
4. ~~PROFIT!~~
**Screenshot:**
 before Commit that I did not make. | git *as-designed |
Type: <b>Performance Issue</b>
When I open any folder to work on in VSC, I get a popup in lower right hand corner that reads:
"The git repository at C:\Users\Darrell has too many active changes, only a subset of Git features will be enabled. Source: Git Extension."
When I click on Source Control, I get a similar m... | 1.0 | Too many files staged for changes (10K+) before Commit that I did not make. -
Type: <b>Performance Issue</b>
When I open any folder to work on in VSC, I get a popup in lower right hand corner that reads:
"The git repository at C:\Users\Darrell has too many active changes, only a subset of Git features will be enabled... | non_priority | too many files staged for changes before commit that i did not make type performance issue when i open any folder to work on in vsc i get a popup in lower right hand corner that reads the git repository at c users darrell has too many active changes only a subset of git features will be enabled sour... | 0 |
14,524 | 3,274,567,279 | IssuesEvent | 2015-10-26 11:38:52 | owncloud/client | https://api.github.com/repos/owncloud/client | closed | Unclear String "Discovering 'ownCloud'" in account settings | Design & UX ReadyToTest | It is very unclear what it means when the owncloud client is doing when it says "Discovering 'ownCloud'".
Is it looking through files in the local computer, is it waiting for the server?

I hope something more... | 1.0 | Unclear String "Discovering 'ownCloud'" in account settings - It is very unclear what it means when the owncloud client is doing when it says "Discovering 'ownCloud'".
Is it looking through files in the local computer, is it waiting for the server?
 | documentation feature | **Is your feature request related to a problem? Please describe.**
We have hit a wall with the types of aggregation we can make. There are too many repositories and we can not show all their aggregations together without breaking the api. See https://github.com/datacite/datacite/issues/958
We would need to remove... | 1.0 | Proposal to change navigation in stats portal (without repository tab) - **Is your feature request related to a problem? Please describe.**
We have hit a wall with the types of aggregation we can make. There are too many repositories and we can not show all their aggregations together without breaking the api. See h... | non_priority | proposal to change navigation in stats portal without repository tab is your feature request related to a problem please describe we have hit a wall with the types of aggregation we can make there are too many repositories and we can not show all their aggregations together without breaking the api see ... | 0 |
195,481 | 14,730,970,150 | IssuesEvent | 2021-01-06 14:02:29 | opendatapolicing/opendatapolicing | https://api.github.com/repos/opendatapolicing/opendatapolicing | opened | Create the SiteState Java class | create_java_class_SiteState | # Mission SiteState Java class

Your mission, should you choose to accept it, is to create a new Java class SiteStateGen.
The [Southern Coalition for Social J... | 1.0 | Create the SiteState Java class - # Mission SiteState Java class

Your mission, should you choose to accept it, is to create a new Java class SiteStateGen.
Th... | non_priority | create the sitestate java class mission sitestate java class mission impossible open data policing your mission should you choose to accept it is to create a new java class sitestategen the needs you to solve one of the world s most challenging problems to aggregate visualize and publish... | 0 |
331,335 | 24,303,192,743 | IssuesEvent | 2022-09-29 15:16:32 | mckinleypadgett/Donaldson-YouTube-Analysis | https://api.github.com/repos/mckinleypadgett/Donaldson-YouTube-Analysis | opened | Update Use-Case Diagram | documentation ToDo | Update the use-case diagram from iteration 1 with the advice Dr. Dogdu gave in class. When finished, lets ping him with an email so he can check/ approve of this new update. | 1.0 | Update Use-Case Diagram - Update the use-case diagram from iteration 1 with the advice Dr. Dogdu gave in class. When finished, lets ping him with an email so he can check/ approve of this new update. | non_priority | update use case diagram update the use case diagram from iteration with the advice dr dogdu gave in class when finished lets ping him with an email so he can check approve of this new update | 0 |
297,286 | 22,347,987,480 | IssuesEvent | 2022-06-15 09:28:43 | spring-projects/spring-framework | https://api.github.com/repos/spring-projects/spring-framework | closed | Fix Kotlin example for @ComponentScan basePackages attribute | type: documentation in: kotlin | https://docs.spring.io/spring-framework/docs/current/reference/html/core.html#beans-scanning-filters
kotlin to:
```kotlin
@Configuration
@ComponentScan(basePackages = ["org.example"],
includeFilters = [Filter(type = FilterType.REGEX, pattern = [".*Stub.*Repository"])],
excludeFilters = [Filte... | 1.0 | Fix Kotlin example for @ComponentScan basePackages attribute - https://docs.spring.io/spring-framework/docs/current/reference/html/core.html#beans-scanning-filters
kotlin to:
```kotlin
@Configuration
@ComponentScan(basePackages = ["org.example"],
includeFilters = [Filter(type = FilterType.REGEX, patte... | non_priority | fix kotlin example for componentscan basepackages attribute kotlin to kotlin configuration componentscan basepackages includefilters excludefilters class appconfig | 0 |
121,142 | 15,861,074,212 | IssuesEvent | 2021-04-08 09:53:45 | ArchiveBox/ArchiveBox | https://api.github.com/repos/ArchiveBox/ArchiveBox | opened | Show prompt to update in Web UI when ArchiveBox version is out of date | difficulty: easy good first ticket is: enhancement javascript status: design phase | Many people seem to be running older versions, which can lead to trouble when upgrading many versions at a time.
I'd like to nudge people towards upgrading more frequently by showing something in the UI.
Possibly using: https://github.com/releasepage/version.js | 1.0 | Show prompt to update in Web UI when ArchiveBox version is out of date - Many people seem to be running older versions, which can lead to trouble when upgrading many versions at a time.
I'd like to nudge people towards upgrading more frequently by showing something in the UI.
Possibly using: https://github.com/re... | non_priority | show prompt to update in web ui when archivebox version is out of date many people seem to be running older versions which can lead to trouble when upgrading many versions at a time i d like to nudge people towards upgrading more frequently by showing something in the ui possibly using | 0 |
143,366 | 11,545,408,089 | IssuesEvent | 2020-02-18 13:23:40 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | closed | WriteBehindEntryStoreQueueReplicationTest.queued_entries_with_expirationTimes_are_replicated_when_cluster_scaled | Module: IMap Source: Internal Team: Core Type: Test-Failure | http://jenkins.hazelcast.com/job/Hazelcast-pr-builder/4021/testReport/junit/com.hazelcast.map.impl.mapstore.writebehind/WriteBehindEntryStoreQueueReplicationTest/queued_entries_with_expirationTimes_are_replicated_when_cluster_scaled_up/
```
java.lang.AssertionError: Expected 'expirationTime' to be between 157201164... | 1.0 | WriteBehindEntryStoreQueueReplicationTest.queued_entries_with_expirationTimes_are_replicated_when_cluster_scaled - http://jenkins.hazelcast.com/job/Hazelcast-pr-builder/4021/testReport/junit/com.hazelcast.map.impl.mapstore.writebehind/WriteBehindEntryStoreQueueReplicationTest/queued_entries_with_expirationTimes_are_rep... | non_priority | writebehindentrystorequeuereplicationtest queued entries with expirationtimes are replicated when cluster scaled java lang assertionerror expected expirationtime to be between and but was at org junit assert fail assert java at org junit assert asserttrue assert java at com hazelcast t... | 0 |
7,012 | 7,837,404,825 | IssuesEvent | 2018-06-18 05:55:01 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | How do we add metadata in the QnAMaker knowledge base document? | assigned-to-author cognitive-services/svc product-question triaged | Is there a way to add meta data to knowledge base document from which the QnA's are extracted? Or adding them manually through QnAMaker website the only option?
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: cb1d6a8c-954c-9ce8-6101-c19b2072... | 1.0 | How do we add metadata in the QnAMaker knowledge base document? - Is there a way to add meta data to knowledge base document from which the QnA's are extracted? Or adding them manually through QnAMaker website the only option?
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.co... | non_priority | how do we add metadata in the qnamaker knowledge base document is there a way to add meta data to knowledge base document from which the qna s are extracted or adding them manually through qnamaker website the only option document details ⚠ do not edit this section it is required for docs microsoft co... | 0 |
34,381 | 6,320,475,541 | IssuesEvent | 2017-07-25 01:47:33 | zcash/zcash | https://api.github.com/repos/zcash/zcash | closed | Cannot send to t-addr | documentation user support wallet | zcash compiled on two Debian 8.6 machines, g++ (Debian 4.9.2-10) 4.9.2 and mining. Mined two blocks on one and tried to send money to the other, but got an error. Then tried sending between addresses on the same machine, still no-go. In the following, `zcli` is an alias for `zcash-cli`
```
jank@debian-modeli:~/zminer$... | 1.0 | Cannot send to t-addr - zcash compiled on two Debian 8.6 machines, g++ (Debian 4.9.2-10) 4.9.2 and mining. Mined two blocks on one and tried to send money to the other, but got an error. Then tried sending between addresses on the same machine, still no-go. In the following, `zcli` is an alias for `zcash-cli`
```
jank... | non_priority | cannot send to t addr zcash compiled on two debian machines g debian and mining mined two blocks on one and tried to send money to the other but got an error then tried sending between addresses on the same machine still no go in the following zcli is an alias for zcash cli jank ... | 0 |
92,204 | 8,355,346,927 | IssuesEvent | 2018-10-02 15:28:52 | paulkaefer/sandbox | https://api.github.com/repos/paulkaefer/sandbox | closed | here's an issue that will have two comments, and then be closed | help wanted test | Description of the issue here.
We might need to change `print "Hello, world!"` to `print("Hello, world!")` to be compatible with Python 3.
See [test.py](https://github.com/paulkaefer/sandbox/blob/master/test.py) from revision 913acef6b4fa. | 1.0 | here's an issue that will have two comments, and then be closed - Description of the issue here.
We might need to change `print "Hello, world!"` to `print("Hello, world!")` to be compatible with Python 3.
See [test.py](https://github.com/paulkaefer/sandbox/blob/master/test.py) from revision 913acef6b4fa. | non_priority | here s an issue that will have two comments and then be closed description of the issue here we might need to change print hello world to print hello world to be compatible with python see from revision | 0 |
202,474 | 15,286,650,535 | IssuesEvent | 2021-02-23 14:56:08 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: alterpk-tpcc-500 failed | C-test-failure O-roachtest O-robot branch-release-20.1 release-blocker | [(roachtest).alterpk-tpcc-500 failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2661563&tab=buildLog) on [release-20.1@90f78268f3b5b08ba838ac3ad164821d2f5a5362](https://github.com/cockroachdb/cockroach/commits/90f78268f3b5b08ba838ac3ad164821d2f5a5362):
```
| /home/agent/work/.go/src/github.com/cockroa... | 2.0 | roachtest: alterpk-tpcc-500 failed - [(roachtest).alterpk-tpcc-500 failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2661563&tab=buildLog) on [release-20.1@90f78268f3b5b08ba838ac3ad164821d2f5a5362](https://github.com/cockroachdb/cockroach/commits/90f78268f3b5b08ba838ac3ad164821d2f5a5362):
```
| /home/... | non_priority | roachtest alterpk tpcc failed on home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go main registeralterpk home agent work go src github com cockroachdb cockroach pkg cmd roachtest alterpk go main monitor go home agent ... | 0 |
137,427 | 18,752,710,248 | IssuesEvent | 2021-11-05 05:52:41 | madhans23/linux-4.15 | https://api.github.com/repos/madhans23/linux-4.15 | opened | CVE-2018-19407 (Medium) detected in linuxv4.15 | security vulnerability | ## CVE-2018-19407 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv4.15</b></p></summary>
<p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/brodo... | True | CVE-2018-19407 (Medium) detected in linuxv4.15 - ## CVE-2018-19407 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv4.15</b></p></summary>
<p>
<p>Library home page: <a href=http... | non_priority | cve medium detected in cve medium severity vulnerability vulnerable library library home page a href found in head commit a href found in base branch master vulnerable source files arch kvm c vulnerability details ... | 0 |
116,623 | 24,952,595,649 | IssuesEvent | 2022-11-01 08:49:52 | Regalis11/Barotrauma | https://api.github.com/repos/Regalis11/Barotrauma | closed | Strings localization of the RussianVanillaEditorTexts.xml is not applied in the editor | Code Modding | ### Disclaimers
- [X] I have searched the issue tracker to check if the issue has already been reported.
- [ ] My issue happened while using mods.
### What happened?
There is no translation in the game editor. The required translation strings exist in the `RussianVanillaEditorTexts.xml` file, but you must pla... | 1.0 | Strings localization of the RussianVanillaEditorTexts.xml is not applied in the editor - ### Disclaimers
- [X] I have searched the issue tracker to check if the issue has already been reported.
- [ ] My issue happened while using mods.
### What happened?
There is no translation in the game editor. The require... | non_priority | strings localization of the russianvanillaeditortexts xml is not applied in the editor disclaimers i have searched the issue tracker to check if the issue has already been reported my issue happened while using mods what happened there is no translation in the game editor the required tr... | 0 |
48,194 | 13,067,513,374 | IssuesEvent | 2020-07-31 00:42:12 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | closed | [simulation] error in MC afterprocessing (MCPulseSeriesParticleIDMap) (Trac #1942) | Migrated from Trac combo simulation defect | I was again on the search for simulation of some MCstudies, for which I need the complete I3MCPulse-info (MCPulseMap, ParticleIDMap and I3MCTRee); It took me some while to locate an appropriate one, which I found in dataset 11843 resp. 11642 (IC86:2013 GENIE simulation), one of the latest produced datasets
This datase... | 1.0 | [simulation] error in MC afterprocessing (MCPulseSeriesParticleIDMap) (Trac #1942) - I was again on the search for simulation of some MCstudies, for which I need the complete I3MCPulse-info (MCPulseMap, ParticleIDMap and I3MCTRee); It took me some while to locate an appropriate one, which I found in dataset 11843 resp.... | non_priority | error in mc afterprocessing mcpulseseriesparticleidmap trac i was again on the search for simulation of some mcstudies for which i need the complete info mcpulsemap particleidmap and it took me some while to locate an appropriate one which i found in dataset resp genie simulation one of... | 0 |
40,508 | 5,225,743,488 | IssuesEvent | 2017-01-27 19:12:34 | phetsims/tasks | https://api.github.com/repos/phetsims/tasks | closed | artwork for wolf in Natural Selection | design:artwork | I need a wolf drawn in illustrator. The original looked like this:

When the wolves get small on the screen the black stroke around them doesn't look great, so less detail there w... | 1.0 | artwork for wolf in Natural Selection - I need a wolf drawn in illustrator. The original looked like this:

When the wolves get small on the screen the black stroke around them do... | non_priority | artwork for wolf in natural selection i need a wolf drawn in illustrator the original looked like this when the wolves get small on the screen the black stroke around them doesn t look great so less detail there would be nice it doesn t need to look exactly like the original | 0 |
63,462 | 14,656,729,415 | IssuesEvent | 2020-12-28 14:04:11 | fu1771695yongxie/plyr | https://api.github.com/repos/fu1771695yongxie/plyr | opened | CVE-2018-11694 (High) detected in opennmsopennms-source-26.0.0-1, node-sass-4.14.1.tgz | security vulnerability | ## CVE-2018-11694 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>opennmsopennms-source-26.0.0-1</b>, <b>node-sass-4.14.1.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.1... | True | CVE-2018-11694 (High) detected in opennmsopennms-source-26.0.0-1, node-sass-4.14.1.tgz - ## CVE-2018-11694 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>opennmsopennms-source-26.0.0... | non_priority | cve high detected in opennmsopennms source node sass tgz cve high severity vulnerability vulnerable libraries opennmsopennms source node sass tgz node sass tgz wrapper around libsass library home page a href path to dependency file ply... | 0 |
247,997 | 26,771,169,450 | IssuesEvent | 2023-01-31 14:13:44 | xinYG/monorepo | https://api.github.com/repos/xinYG/monorepo | opened | CVE-2022-25881 (Medium) detected in http-cache-semantics-4.1.0.tgz | security vulnerability | ## CVE-2022-25881 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>http-cache-semantics-4.1.0.tgz</b></p></summary>
<p>Parses Cache-Control and other headers. Helps building correct H... | True | CVE-2022-25881 (Medium) detected in http-cache-semantics-4.1.0.tgz - ## CVE-2022-25881 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>http-cache-semantics-4.1.0.tgz</b></p></summary>... | non_priority | cve medium detected in http cache semantics tgz cve medium severity vulnerability vulnerable library http cache semantics tgz parses cache control and other headers helps building correct http caches and proxies library home page a href dependency hierarchy zgri... | 0 |
138,919 | 18,796,863,341 | IssuesEvent | 2021-11-08 23:46:26 | Dima2022/DiscountsApp | https://api.github.com/repos/Dima2022/DiscountsApp | opened | WS-2019-0427 (Medium) detected in elliptic-6.5.0.tgz | security vulnerability | ## WS-2019-0427 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.5.0.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/... | True | WS-2019-0427 (Medium) detected in elliptic-6.5.0.tgz - ## WS-2019-0427 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.5.0.tgz</b></p></summary>
<p>EC cryptography</p>
<p>... | non_priority | ws medium detected in elliptic tgz ws medium severity vulnerability vulnerable library elliptic tgz ec cryptography library home page a href path to dependency file discountsapp scndisc frontend scndisc admin ui package json path to vulnerable library discountsapp sc... | 0 |
76,654 | 21,527,525,859 | IssuesEvent | 2022-04-28 20:04:30 | envoyproxy/envoy | https://api.github.com/repos/envoyproxy/envoy | closed | v1.19 CI is failing on macos | area/build stale area/ci | It seems the macos failure is unrelated
```
ERROR: /Users/runner/work/1/s/source/exe/BUILD:23:16: Linking source/exe/envoy-static failed: (Aborted): cc_wrapper.sh failed: error executing command
(cd /private/var/tmp/_bazel_runner/3d1a7f52fd47fc9a8db71770aacd13e5/sandbox/darwin-sandbox/3950/execroot/envoy && \
... | 1.0 | v1.19 CI is failing on macos - It seems the macos failure is unrelated
```
ERROR: /Users/runner/work/1/s/source/exe/BUILD:23:16: Linking source/exe/envoy-static failed: (Aborted): cc_wrapper.sh failed: error executing command
(cd /private/var/tmp/_bazel_runner/3d1a7f52fd47fc9a8db71770aacd13e5/sandbox/darwin-san... | non_priority | ci is failing on macos it seems the macos failure is unrelated error users runner work s source exe build linking source exe envoy static failed aborted cc wrapper sh failed error executing command cd private var tmp bazel runner sandbox darwin sandbox execroot envoy exec ... | 0 |
28,068 | 8,070,985,355 | IssuesEvent | 2018-08-06 11:40:16 | pyzo/pyzo | https://api.github.com/repos/pyzo/pyzo | closed | Flatpak package | part: building and distribution type: enhancement | It would be great to have a flatpack package for pyzo, so every linux user could use it. | 1.0 | Flatpak package - It would be great to have a flatpack package for pyzo, so every linux user could use it. | non_priority | flatpak package it would be great to have a flatpack package for pyzo so every linux user could use it | 0 |
42,097 | 12,876,631,464 | IssuesEvent | 2020-07-11 06:11:15 | whatwg/html | https://api.github.com/repos/whatwg/html | closed | Consolidate performing a security check in the spec with implementations | security/privacy | https://html.spec.whatwg.org/multipage/browsers.html#integration-with-idl
> If IsPlatformObjectSameOrigin\(platformObject\) is false, then throw a "SecurityError" DOMException\.
Blink currently doesn't implement this step in all cases, while Gecko is more strict by also applying the check to non-platform objects ... | True | Consolidate performing a security check in the spec with implementations - https://html.spec.whatwg.org/multipage/browsers.html#integration-with-idl
> If IsPlatformObjectSameOrigin\(platformObject\) is false, then throw a "SecurityError" DOMException\.
Blink currently doesn't implement this step in all cases, whi... | non_priority | consolidate performing a security check in the spec with implementations if isplatformobjectsameorigin platformobject is false then throw a securityerror domexception blink currently doesn t implement this step in all cases while gecko is more strict by also applying the check to non platform objec... | 0 |
59,577 | 8,372,097,313 | IssuesEvent | 2018-10-05 04:59:21 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | Request: Hardening instructions | area/documentation kind/question status/autoclosed | A dedicated hardening guide or tips for Rancher(OS) would be great. A central and up to date write up would help newcomers and even other users to check if they have Rancher(OS) set up correctly and securely.
Thoughts? | 1.0 | Request: Hardening instructions - A dedicated hardening guide or tips for Rancher(OS) would be great. A central and up to date write up would help newcomers and even other users to check if they have Rancher(OS) set up correctly and securely.
Thoughts? | non_priority | request hardening instructions a dedicated hardening guide or tips for rancher os would be great a central and up to date write up would help newcomers and even other users to check if they have rancher os set up correctly and securely thoughts | 0 |
153,775 | 19,708,593,493 | IssuesEvent | 2022-01-13 01:43:41 | artsking/linux-4.19.72_CVE-2020-14386 | https://api.github.com/repos/artsking/linux-4.19.72_CVE-2020-14386 | opened | CVE-2020-25673 (Medium) detected in linux-yoctov5.4.51 | security vulnerability | ## CVE-2020-25673 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://gi... | True | CVE-2020-25673 (Medium) detected in linux-yoctov5.4.51 - ## CVE-2020-25673 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Emb... | non_priority | cve medium detected in linux cve medium severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in base branch master vulnerable source files net nfc llcp sock c net nfc llcp sock ... | 0 |
211,953 | 23,856,852,427 | IssuesEvent | 2022-09-07 01:09:59 | mattdanielbrown/yo-webapp-2022 | https://api.github.com/repos/mattdanielbrown/yo-webapp-2022 | opened | mocha-9.2.0.tgz: 1 vulnerabilities (highest severity is: 7.5) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mocha-9.2.0.tgz</b></p></summary>
<p>simple, flexible, fun test framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/mocha/-/mocha-9.2.0.tgz">https... | True | mocha-9.2.0.tgz: 1 vulnerabilities (highest severity is: 7.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mocha-9.2.0.tgz</b></p></summary>
<p>simple, flexible, fun test framework</p>
<p>Library home page: <a... | non_priority | mocha tgz vulnerabilities highest severity is vulnerable library mocha tgz simple flexible fun test framework library home page a href path to dependency file package json path to vulnerable library node modules mocha package json found in head commit a href ... | 0 |
79,180 | 9,851,831,642 | IssuesEvent | 2019-06-19 11:24:44 | dart-lang/sdk | https://api.github.com/repos/dart-lang/sdk | closed | [vm/ffi] struct inheritance | area-vm library-ffi type-design | Should we allow subtyping of structs?
```dart
import dart:ffi show Struct, Int8;
A extends Struct {
@Int8()
int x;
}
B extends A {
@Int8()
int y;
}
```
Where `B` has all the fields of `A`.
/cc @sjindel-google | 1.0 | [vm/ffi] struct inheritance - Should we allow subtyping of structs?
```dart
import dart:ffi show Struct, Int8;
A extends Struct {
@Int8()
int x;
}
B extends A {
@Int8()
int y;
}
```
Where `B` has all the fields of `A`.
/cc @sjindel-google | non_priority | struct inheritance should we allow subtyping of structs dart import dart ffi show struct a extends struct int x b extends a int y where b has all the fields of a cc sjindel google | 0 |
383,832 | 26,565,871,533 | IssuesEvent | 2023-01-20 20:09:42 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | Normalmap on a generated Mesh does not work | topic:rendering good first issue documentation topic:3d | ### Godot version
3.3.3
### System information
Archlinux GLES3 Nvidia Geforce GTX 1650 Super
### Issue description
On a generated mesh, a shader can't use normalmap
### Steps to reproduce
Generate a mesh through code, assign a shader to it
### Minimal reproduction project
https://ufile.io/chdui... | 1.0 | Normalmap on a generated Mesh does not work - ### Godot version
3.3.3
### System information
Archlinux GLES3 Nvidia Geforce GTX 1650 Super
### Issue description
On a generated mesh, a shader can't use normalmap
### Steps to reproduce
Generate a mesh through code, assign a shader to it
### Minima... | non_priority | normalmap on a generated mesh does not work godot version system information archlinux nvidia geforce gtx super issue description on a generated mesh a shader can t use normalmap steps to reproduce generate a mesh through code assign a shader to it minimal repro... | 0 |
5,266 | 5,581,727,888 | IssuesEvent | 2017-03-28 19:33:56 | rye/krye.io | https://api.github.com/repos/rye/krye.io | closed | Environment Hash for Request Caching | concerns:security/client concerns:security/server platform:server | As part of the complete overhaul, (#106) I've come to decide that certain requests will need to be cached in certain ways:
* **Sensitive Data**, like user-specific views, should be cached by user ID, session ID.
* **Time-Sensitive Data**, like volatile views like RSS feeds, should not be cached.
* **Generated Data... | True | Environment Hash for Request Caching - As part of the complete overhaul, (#106) I've come to decide that certain requests will need to be cached in certain ways:
* **Sensitive Data**, like user-specific views, should be cached by user ID, session ID.
* **Time-Sensitive Data**, like volatile views like RSS feeds, sh... | non_priority | environment hash for request caching as part of the complete overhaul i ve come to decide that certain requests will need to be cached in certain ways sensitive data like user specific views should be cached by user id session id time sensitive data like volatile views like rss feeds shou... | 0 |
126,162 | 17,868,886,819 | IssuesEvent | 2021-09-06 13:01:28 | fasttrack-solutions/go-mysql-elasticsearch | https://api.github.com/repos/fasttrack-solutions/go-mysql-elasticsearch | opened | CVE-2020-11022 (Medium) detected in github.com/smartystreets/goconvey-v1.6.4 | security vulnerability | ## CVE-2020-11022 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/smartystreets/goconvey-v1.6.4</b></p></summary>
<p>Go testing in the browser. Integrates with `go test`. ... | True | CVE-2020-11022 (Medium) detected in github.com/smartystreets/goconvey-v1.6.4 - ## CVE-2020-11022 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/smartystreets/goconvey-v1.6... | non_priority | cve medium detected in github com smartystreets goconvey cve medium severity vulnerability vulnerable library github com smartystreets goconvey go testing in the browser integrates with go test write behavioral tests in go dependency hierarchy github com go ... | 0 |
14,733 | 3,420,224,942 | IssuesEvent | 2015-12-08 13:57:11 | astropy/halotools | https://api.github.com/repos/astropy/halotools | closed | Test suite has doubled in runtime | mock-observables testing | Presumably this is because the default settings for the pair counter were set to use Lbox/10 rather than Rmax?
CC @duncandc | 1.0 | Test suite has doubled in runtime - Presumably this is because the default settings for the pair counter were set to use Lbox/10 rather than Rmax?
CC @duncandc | non_priority | test suite has doubled in runtime presumably this is because the default settings for the pair counter were set to use lbox rather than rmax cc duncandc | 0 |
335,989 | 24,485,289,996 | IssuesEvent | 2022-10-09 10:54:10 | xybor-x/xylog | https://api.github.com/repos/xybor-x/xylog | opened | Add Q&A section | documentation | **Problem**
Many people need to know some information about this library.
**Solution**
Add Q&A
| 1.0 | Add Q&A section - **Problem**
Many people need to know some information about this library.
**Solution**
Add Q&A
| non_priority | add q a section problem many people need to know some information about this library solution add q a | 0 |
161,136 | 20,120,414,568 | IssuesEvent | 2022-02-08 01:16:41 | arohablue/BlockDockServer | https://api.github.com/repos/arohablue/BlockDockServer | closed | CVE-2021-20190 (High) detected in jackson-databind-2.8.8.jar - autoclosed | security vulnerability | ## CVE-2021-20190 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2021-20190 (High) detected in jackson-databind-2.8.8.jar - autoclosed - ## CVE-2021-20190 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.8.jar</b></p></summary... | non_priority | cve high detected in jackson databind jar autoclosed cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file blockdockserver b... | 0 |
288,519 | 21,708,914,824 | IssuesEvent | 2022-05-10 12:16:45 | external-secrets/external-secrets | https://api.github.com/repos/external-secrets/external-secrets | closed | Docs site should default to the latest release | kind/bug area/documentation | **Describe the solution you'd like**
tl;dr - the docs site should default to the latest release OR it should always include the version drop down.
Today I was working on getting SecretStores to work with JWT Auth and Vault. I was primarily looking at the docs from https://external-secrets.io/provider-hashicorp-va... | 1.0 | Docs site should default to the latest release - **Describe the solution you'd like**
tl;dr - the docs site should default to the latest release OR it should always include the version drop down.
Today I was working on getting SecretStores to work with JWT Auth and Vault. I was primarily looking at the docs from ... | non_priority | docs site should default to the latest release describe the solution you d like tl dr the docs site should default to the latest release or it should always include the version drop down today i was working on getting secretstores to work with jwt auth and vault i was primarily looking at the docs from ... | 0 |
185,701 | 21,843,723,533 | IssuesEvent | 2022-05-18 01:03:41 | AlexRogalskiy/gradle-kotlin-sample | https://api.github.com/repos/AlexRogalskiy/gradle-kotlin-sample | closed | CVE-2021-36373 (Medium) detected in ant-1.9.13.jar - autoclosed | security vulnerability | ## CVE-2021-36373 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ant-1.9.13.jar</b></p></summary>
<p>master POM</p>
<p>Library home page: <a href="http://ant.apache.org/">http://ant... | True | CVE-2021-36373 (Medium) detected in ant-1.9.13.jar - autoclosed - ## CVE-2021-36373 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ant-1.9.13.jar</b></p></summary>
<p>master POM</p>... | non_priority | cve medium detected in ant jar autoclosed cve medium severity vulnerability vulnerable library ant jar master pom library home page a href path to dependency file gradle kotlin sample buildsrc build gradle kts path to vulnerable library home wss scanner gradle ca... | 0 |
275,929 | 23,954,419,040 | IssuesEvent | 2022-09-12 13:59:09 | samtools/bcftools | https://api.github.com/repos/samtools/bcftools | closed | -i and -e are not complement when I use query subcommand | requires-test-case | I noticed the result of
`bcftools query -i 'FMT/DP>=20' -f '[%CHROM %POS %SAMPLE\n]' input.vcf`
and
`bcftools query -e 'FMT/DP<20' -f '[%CHROM %POS %SAMPLE\n]' input.vcf`
are not complement.
This occur if only I specified %SAMPLE but %FORMAT tags, so I can avoid it by specifying other %FORMAT tags but... | 1.0 | -i and -e are not complement when I use query subcommand - I noticed the result of
`bcftools query -i 'FMT/DP>=20' -f '[%CHROM %POS %SAMPLE\n]' input.vcf`
and
`bcftools query -e 'FMT/DP<20' -f '[%CHROM %POS %SAMPLE\n]' input.vcf`
are not complement.
This occur if only I specified %SAMPLE but %FORMAT t... | non_priority | i and e are not complement when i use query subcommand i noticed the result of bcftools query i fmt dp f input vcf and bcftools query e fmt dp f input vcf are not complement this occur if only i specified sample but format tags so i can avoid it by specifying other fo... | 0 |
11,280 | 9,049,292,400 | IssuesEvent | 2019-02-12 03:53:21 | dotnet/corefx | https://api.github.com/repos/dotnet/corefx | closed | Once CMake supports VS2019 as the project generator use it if installed | area-Infrastructure enhancement | In: https://github.com/dotnet/corefx/pull/34381 we enabled building and generating the native project with VS2019, but CMake doesn't support VS2019 as the project generator. So we reverted the generator change in: https://github.com/dotnet/corefx/pull/34412
This issue is to track CMake's support for VS2019 and to u... | 1.0 | Once CMake supports VS2019 as the project generator use it if installed - In: https://github.com/dotnet/corefx/pull/34381 we enabled building and generating the native project with VS2019, but CMake doesn't support VS2019 as the project generator. So we reverted the generator change in: https://github.com/dotnet/corefx... | non_priority | once cmake supports as the project generator use it if installed in we enabled building and generating the native project with but cmake doesn t support as the project generator so we reverted the generator change in this issue is to track cmake s support for and to update the generator script ... | 0 |
107,992 | 13,536,268,079 | IssuesEvent | 2020-09-16 08:48:24 | JuliaArrays/StaticArrays.jl | https://api.github.com/repos/JuliaArrays/StaticArrays.jl | closed | SizedArray of SubArray isn't a view | bug design | (on StaticArrays 0.6.4)
```
using StaticArrays
m = eye(3)
vm = view(m, 3, : )
svm = SizedArray{Tuple{size(vm)...}}(vm)
julia> svm.data === vm
false
```
this means that mutating `svm` does not mutate `vm` nor `m`. | 1.0 | SizedArray of SubArray isn't a view - (on StaticArrays 0.6.4)
```
using StaticArrays
m = eye(3)
vm = view(m, 3, : )
svm = SizedArray{Tuple{size(vm)...}}(vm)
julia> svm.data === vm
false
```
this means that mutating `svm` does not mutate `vm` nor `m`. | non_priority | sizedarray of subarray isn t a view on staticarrays using staticarrays m eye vm view m svm sizedarray tuple size vm vm julia svm data vm false this means that mutating svm does not mutate vm nor m | 0 |
410,572 | 27,791,973,762 | IssuesEvent | 2023-03-17 09:37:08 | AbianGustavo/proyecto-ets | https://api.github.com/repos/AbianGustavo/proyecto-ets | closed | Creación del anteproyecto | documentation | Se creará un "anteproyecto.md" en el que se detallará sobre el proyecto. | 1.0 | Creación del anteproyecto - Se creará un "anteproyecto.md" en el que se detallará sobre el proyecto. | non_priority | creación del anteproyecto se creará un anteproyecto md en el que se detallará sobre el proyecto | 0 |
120,907 | 10,141,555,128 | IssuesEvent | 2019-08-03 15:18:05 | kubernetes/kubernetes | https://api.github.com/repos/kubernetes/kubernetes | closed | e2e: support extending the item patching | kind/feature lifecycle/rotten sig/testing | <!-- Please only use this template for submitting enhancement requests -->
**What would you like to be added**:
`test/e2e/framework/create.go` can already be partially extended out-of-tree by extending the factory. But that only covers loading of items not directly supported in-tree. Patching currently cannot be ... | 1.0 | e2e: support extending the item patching - <!-- Please only use this template for submitting enhancement requests -->
**What would you like to be added**:
`test/e2e/framework/create.go` can already be partially extended out-of-tree by extending the factory. But that only covers loading of items not directly suppo... | non_priority | support extending the item patching what would you like to be added test framework create go can already be partially extended out of tree by extending the factory but that only covers loading of items not directly supported in tree patching currently cannot be extended why is this needed ... | 0 |
40,510 | 12,799,552,804 | IssuesEvent | 2020-07-02 15:34:22 | TreyM-WSS/WhiteSource-Demo | https://api.github.com/repos/TreyM-WSS/WhiteSource-Demo | opened | CVE-2016-6797 (High) detected in tomcat-embed-core-8.5.4.jar | security vulnerability | ## CVE-2016-6797 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-8.5.4.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="http://t... | True | CVE-2016-6797 (High) detected in tomcat-embed-core-8.5.4.jar - ## CVE-2016-6797 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-8.5.4.jar</b></p></summary>
<p>Core To... | non_priority | cve high detected in tomcat embed core jar cve high severity vulnerability vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file tmp ws scm whitesource demo pom xml path to vulnerable library home wss s... | 0 |
168,876 | 20,825,737,326 | IssuesEvent | 2022-03-18 20:36:48 | vincenzodistasio97/main | https://api.github.com/repos/vincenzodistasio97/main | closed | CVE-2021-32640 (Medium) detected in multiple libraries - autoclosed | security vulnerability | ## CVE-2021-32640 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ws-6.2.1.tgz</b>, <b>ws-5.2.2.tgz</b>, <b>ws-7.2.3.tgz</b></p></summary>
<p>
<details><summary><b>ws-6.2.1.tgz</b>... | True | CVE-2021-32640 (Medium) detected in multiple libraries - autoclosed - ## CVE-2021-32640 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ws-6.2.1.tgz</b>, <b>ws-5.2.2.tgz</b>, <b>ws-... | non_priority | cve medium detected in multiple libraries autoclosed cve medium severity vulnerability vulnerable libraries ws tgz ws tgz ws tgz ws tgz simple to use blazing fast and thoroughly tested websocket client and server for node js library home page a ... | 0 |
144,762 | 11,631,683,429 | IssuesEvent | 2020-02-28 02:14:25 | dapr/dapr | https://api.github.com/repos/dapr/dapr | opened | [Longhaul Chaos Test] Hashtag Snapshot Service | area/test/chaos | This component will exercise Dapr’s state APIs (not in the context of an Actor). It wakes up every minute and retrieves all keys from Redis state store - not using Dapr’s state APIs, since Dapr does not offer an API to query a range of states from another Dapr application’s state store. Is is expected that only a few d... | 1.0 | [Longhaul Chaos Test] Hashtag Snapshot Service - This component will exercise Dapr’s state APIs (not in the context of an Actor). It wakes up every minute and retrieves all keys from Redis state store - not using Dapr’s state APIs, since Dapr does not offer an API to query a range of states from another Dapr applicatio... | non_priority | hashtag snapshot service this component will exercise dapr’s state apis not in the context of an actor it wakes up every minute and retrieves all keys from redis state store not using dapr’s state apis since dapr does not offer an api to query a range of states from another dapr application’s state store is ... | 0 |
10,648 | 4,075,429,378 | IssuesEvent | 2016-05-29 06:57:44 | DotSpatial/DotSpatial | https://api.github.com/repos/DotSpatial/DotSpatial | closed | Open project not redrawing map if properties is set | bug CodePlex | **This issue was imported from [CodePlex](http://dotspatial.codeplex.com/workitem/200)**
**[worsHound](http://www.codeplex.com/site/users/view/worsHound)** wrote 2011-01-04 at 15:42
The map is not drawn after loading a saved project witch has properties set on a layer, on unique values or Quantities. | 1.0 | Open project not redrawing map if properties is set - **This issue was imported from [CodePlex](http://dotspatial.codeplex.com/workitem/200)**
**[worsHound](http://www.codeplex.com/site/users/view/worsHound)** wrote 2011-01-04 at 15:42
The map is not drawn after loading a saved project witch has properties set on a... | non_priority | open project not redrawing map if properties is set this issue was imported from wrote at the map is not drawn after loading a saved project witch has properties set on a layer on unique values or quantities | 0 |
48,494 | 20,160,361,862 | IssuesEvent | 2022-02-09 20:48:52 | dockstore/dockstore | https://api.github.com/repos/dockstore/dockstore | opened | Restubbing a worklow with a snapshot version returns a 500 error | bug web-service | **Describe the bug**
Restubbing a workflow with a snapshot version returns a 500 error.
**To Reproduce**
Steps to reproduce the behavior:
1. Create a workflow and successfully snapshot a version.
2. Click on 'Restub'.
3. See that nothing happens. No error is displayed in the UI.
4. Check the developer tools to... | 1.0 | Restubbing a worklow with a snapshot version returns a 500 error - **Describe the bug**
Restubbing a workflow with a snapshot version returns a 500 error.
**To Reproduce**
Steps to reproduce the behavior:
1. Create a workflow and successfully snapshot a version.
2. Click on 'Restub'.
3. See that nothing happens... | non_priority | restubbing a worklow with a snapshot version returns a error describe the bug restubbing a workflow with a snapshot version returns a error to reproduce steps to reproduce the behavior create a workflow and successfully snapshot a version click on restub see that nothing happens no... | 0 |
2,339 | 3,786,424,828 | IssuesEvent | 2016-03-21 02:35:29 | openpgpjs/openpgpjs | https://api.github.com/repos/openpgpjs/openpgpjs | opened | Implement ECC support for Curve P-256, P-384, P-521 (RFC6637) | Compatibility Performance Security | See http://tools.ietf.org/html/rfc6637
This issue tracks the implementation of ECDSA and ECDH for "Curve P-256", "Curve P-384", and "Curve P-521". The advantage of these curves is that they have already been standardized for OpenPGP in RFC 6637 and are support natively by both [WebCrypto](https://www.chromium.org/bl... | True | Implement ECC support for Curve P-256, P-384, P-521 (RFC6637) - See http://tools.ietf.org/html/rfc6637
This issue tracks the implementation of ECDSA and ECDH for "Curve P-256", "Curve P-384", and "Curve P-521". The advantage of these curves is that they have already been standardized for OpenPGP in RFC 6637 and are ... | non_priority | implement ecc support for curve p p p see this issue tracks the implementation of ecdsa and ecdh for curve p curve p and curve p the advantage of these curves is that they have already been standardized for openpgp in rfc and are support natively by both and | 0 |
348,394 | 31,561,039,765 | IssuesEvent | 2023-09-03 08:58:18 | gear-foundation/vara-network | https://api.github.com/repos/gear-foundation/vara-network | opened | Faucet claim failed | bug testnet | ### Problem
I requested faucet, but its didnt come
### Steps
1.
2.
3.
### Expected Behavior
_No response_
### Your Substrate Address
5EnDNL75NG3x7bUxX4iQ3c2pppvee8GeFZT2eK44zYwjjHE6
### What browsers are you seeing the problem on?
- [ ] Firefox
- [X] Chrome
- [ ] Safari
- [ ] Microsoft Edge
- [ ] Other
... | 1.0 | Faucet claim failed - ### Problem
I requested faucet, but its didnt come
### Steps
1.
2.
3.
### Expected Behavior
_No response_
### Your Substrate Address
5EnDNL75NG3x7bUxX4iQ3c2pppvee8GeFZT2eK44zYwjjHE6
### What browsers are you seeing the problem on?
- [ ] Firefox
- [X] Chrome
- [ ] Safari
- [ ] Micros... | non_priority | faucet claim failed problem i requested faucet but its didnt come steps expected behavior no response your substrate address what browsers are you seeing the problem on firefox chrome safari microsoft edge other other browser no response ... | 0 |
76,732 | 21,561,778,463 | IssuesEvent | 2022-05-01 09:11:57 | dftd4/dftd4 | https://api.github.com/repos/dftd4/dftd4 | closed | Cc: error: unrecognized command line option ‘-qopenmp’ while compiling dftd4-python with meson | build | Dear developers,
I am trying to compile dftd4-python by meson using the command:
meson setup _build -Dpython_version=3 -Dfortran_link_args=-qopenmp
the output is:
> Using 'PKG_CONFIG_PATH' from environment with value: '/home/gp/tools/dftd4-3.3.0/lib/pkgconfig'
> Using 'PKG_CONFIG_PATH' from environment with ... | 1.0 | Cc: error: unrecognized command line option ‘-qopenmp’ while compiling dftd4-python with meson - Dear developers,
I am trying to compile dftd4-python by meson using the command:
meson setup _build -Dpython_version=3 -Dfortran_link_args=-qopenmp
the output is:
> Using 'PKG_CONFIG_PATH' from environment with va... | non_priority | cc error unrecognized command line option ‘ qopenmp’ while compiling python with meson dear developers i am trying to compile python by meson using the command meson setup build dpython version dfortran link args qopenmp the output is using pkg config path from environment with value h... | 0 |
228,449 | 25,192,544,271 | IssuesEvent | 2022-11-12 04:53:10 | justunsix/confluence-export-pages-to-pdf | https://api.github.com/repos/justunsix/confluence-export-pages-to-pdf | closed | CVE-2022-3517 (High) detected in minimatch-3.0.4.tgz - autoclosed | security vulnerability | ## CVE-2022-3517 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimatch-3.0.4.tgz</b></p></summary>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://regist... | True | CVE-2022-3517 (High) detected in minimatch-3.0.4.tgz - autoclosed - ## CVE-2022-3517 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimatch-3.0.4.tgz</b></p></summary>
<p>a glob mat... | non_priority | cve high detected in minimatch tgz autoclosed cve high severity vulnerability vulnerable library minimatch tgz a glob matcher in javascript library home page a href path to dependency file node option package json path to vulnerable library node option node modul... | 0 |
133,507 | 18,298,890,205 | IssuesEvent | 2021-10-05 23:43:42 | ghc-dev/Danielle-Mosley | https://api.github.com/repos/ghc-dev/Danielle-Mosley | closed | CVE-2021-21290 (Medium) detected in netty-handler-4.1.39.Final.jar, netty-codec-http-4.1.39.Final.jar - autoclosed | security vulnerability | ## CVE-2021-21290 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>netty-handler-4.1.39.Final.jar</b>, <b>netty-codec-http-4.1.39.Final.jar</b></p></summary>
<p>
<details><summary><... | True | CVE-2021-21290 (Medium) detected in netty-handler-4.1.39.Final.jar, netty-codec-http-4.1.39.Final.jar - autoclosed - ## CVE-2021-21290 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <... | non_priority | cve medium detected in netty handler final jar netty codec http final jar autoclosed cve medium severity vulnerability vulnerable libraries netty handler final jar netty codec http final jar netty handler final jar netty is an asynchronous event ... | 0 |
51,678 | 10,710,809,161 | IssuesEvent | 2019-10-25 03:44:25 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | Privacy: Information Requests - Can able to save invalid email string | No Code Attached Yet | ### Steps to reproduce the issue
1. Go to the Admin-> Users-> Privacy-> Request
2. Click on New and add invalid email string in the Email field and save it.
3. The record get save and the system shows the warning and item saved message at a time.
### Expected result
The system should not allow saving invalid e... | 1.0 | Privacy: Information Requests - Can able to save invalid email string - ### Steps to reproduce the issue
1. Go to the Admin-> Users-> Privacy-> Request
2. Click on New and add invalid email string in the Email field and save it.
3. The record get save and the system shows the warning and item saved message at a time... | non_priority | privacy information requests can able to save invalid email string steps to reproduce the issue go to the admin users privacy request click on new and add invalid email string in the email field and save it the record get save and the system shows the warning and item saved message at a time... | 0 |
140,244 | 18,900,639,068 | IssuesEvent | 2021-11-16 00:14:15 | pustovitDmytro/code-chronicle | https://api.github.com/repos/pustovitDmytro/code-chronicle | opened | CVE-2021-23807 (High) detected in jsonpointer-4.1.0.tgz | security vulnerability | ## CVE-2021-23807 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jsonpointer-4.1.0.tgz</b></p></summary>
<p>Simple JSON Addressing.</p>
<p>Library home page: <a href="https://registry... | True | CVE-2021-23807 (High) detected in jsonpointer-4.1.0.tgz - ## CVE-2021-23807 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jsonpointer-4.1.0.tgz</b></p></summary>
<p>Simple JSON Addre... | non_priority | cve high detected in jsonpointer tgz cve high severity vulnerability vulnerable library jsonpointer tgz simple json addressing library home page a href path to dependency file code chronicle package json path to vulnerable library code chronicle node modules jsonpoi... | 0 |
19,149 | 6,676,465,483 | IssuesEvent | 2017-10-05 05:54:13 | habitat-sh/habitat | https://api.github.com/repos/habitat-sh/habitat | closed | Scrub creds from worker logs | A-builder C-chore E-easy L-rust | We need to strip secure info from any builder logs so that it doesn't inadvertently end up in log aggregation in the future. | 1.0 | Scrub creds from worker logs - We need to strip secure info from any builder logs so that it doesn't inadvertently end up in log aggregation in the future. | non_priority | scrub creds from worker logs we need to strip secure info from any builder logs so that it doesn t inadvertently end up in log aggregation in the future | 0 |
220,630 | 16,978,006,948 | IssuesEvent | 2021-06-30 03:55:14 | shandley/hecatomb | https://api.github.com/repos/shandley/hecatomb | closed | How to convert fastq-dumps to R1 /R2 | documentation enhancement | Since we use _R1 and _R2 to find mate pairs, here is how to convert fastq-dump output to R1/R2 format
```
for F in *; do O=$(echo $F | sed -e 's/pass_/pass_R/'); echo $F $O; mv $F $O; done
```
We should add this to the wiki | 1.0 | How to convert fastq-dumps to R1 /R2 - Since we use _R1 and _R2 to find mate pairs, here is how to convert fastq-dump output to R1/R2 format
```
for F in *; do O=$(echo $F | sed -e 's/pass_/pass_R/'); echo $F $O; mv $F $O; done
```
We should add this to the wiki | non_priority | how to convert fastq dumps to since we use and to find mate pairs here is how to convert fastq dump output to format for f in do o echo f sed e s pass pass r echo f o mv f o done we should add this to the wiki | 0 |
445,935 | 31,388,119,118 | IssuesEvent | 2023-08-26 02:19:30 | vercel/next.js | https://api.github.com/repos/vercel/next.js | closed | Docs: Potentially wrong example (because `export const revalidate` might not work outside special files) | template: documentation | ### What is the improvement or update you wish to see?
In the documentation page linked below there is this example
```tsx
// utils/get-item.ts
import { cache } from 'react'
export const revalidate = 3600 // revalidate the data at most every hour
export const getItem = cache(async (id: string) => {
con... | 1.0 | Docs: Potentially wrong example (because `export const revalidate` might not work outside special files) - ### What is the improvement or update you wish to see?
In the documentation page linked below there is this example
```tsx
// utils/get-item.ts
import { cache } from 'react'
export const revalidate = 360... | non_priority | docs potentially wrong example because export const revalidate might not work outside special files what is the improvement or update you wish to see in the documentation page linked below there is this example tsx utils get item ts import cache from react export const revalidate ... | 0 |
44,958 | 18,290,508,627 | IssuesEvent | 2021-10-05 14:47:58 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | opened | Meeting: Parking Enforcement Sprint Review | Workgroup: PE Service: Apps Service: Product Product: Parking Enterprise Portal | Demo prototype to Parking Enforcement team
Parking Enforcement Officers will be entering the new SR's for Parking Meters Non 311 SR's
Meeting scheduled for 10/7 | 2.0 | Meeting: Parking Enforcement Sprint Review - Demo prototype to Parking Enforcement team
Parking Enforcement Officers will be entering the new SR's for Parking Meters Non 311 SR's
Meeting scheduled for 10/7 | non_priority | meeting parking enforcement sprint review demo prototype to parking enforcement team parking enforcement officers will be entering the new sr s for parking meters non sr s meeting scheduled for | 0 |
57,570 | 24,152,764,758 | IssuesEvent | 2022-09-22 03:42:21 | hashicorp/terraform-provider-aws | https://api.github.com/repos/hashicorp/terraform-provider-aws | closed | N/A - Closed | service/route53 needs-triage | ### Terraform Core Version
0.13.7
### AWS Provider Version
4.31.0
### Affected Resource(s)
```
```
### Expected Behavior
### Actual Behavior
```
```
### Relevant Error/Panic Output Snippet
### Terraform Configuration Files
### Steps to Reproduce
### Debug Output
_No re... | 1.0 | N/A - Closed - ### Terraform Core Version
0.13.7
### AWS Provider Version
4.31.0
### Affected Resource(s)
```
```
### Expected Behavior
### Actual Behavior
```
```
### Relevant Error/Panic Output Snippet
### Terraform Configuration Files
### Steps to Reproduce
### Debug O... | non_priority | n a closed terraform core version aws provider version affected resource s expected behavior actual behavior relevant error panic output snippet terraform configuration files steps to reproduce debug out... | 0 |
52,902 | 27,822,278,574 | IssuesEvent | 2023-03-19 11:27:10 | iboB/dynamix | https://api.github.com/repos/iboB/dynamix | opened | Extract `object_mixin_data` management from `object_mutation` | performance | `object::clear_mixin_data` is `noexcept`, but relies on an `noexcept(false)` destructor. It should never throw in the given case, but still the compiler will generate calls to `std::terminate` there. It is possible to create a class `basic_object_mutation` which provides alloc/dealloc/destroy functions for mixin data. ... | True | Extract `object_mixin_data` management from `object_mutation` - `object::clear_mixin_data` is `noexcept`, but relies on an `noexcept(false)` destructor. It should never throw in the given case, but still the compiler will generate calls to `std::terminate` there. It is possible to create a class `basic_object_mutation`... | non_priority | extract object mixin data management from object mutation object clear mixin data is noexcept but relies on an noexcept false destructor it should never throw in the given case but still the compiler will generate calls to std terminate there it is possible to create a class basic object mutation ... | 0 |
184,083 | 31,817,046,410 | IssuesEvent | 2023-09-13 21:22:50 | department-of-veterans-affairs/vets-design-system-documentation | https://api.github.com/repos/department-of-veterans-affairs/vets-design-system-documentation | opened | Tokens - Add Hub colors | platform-design-system-team | ## Description
These color variables need to be added as tokens:
$red-70v: #8b1303;
$red-60v: #b51d09;
$indigo-cool-60: #3f57a6;
$red-60: #a23737;
$mint-cool-50: #21827f;
$orange-warm-50: #bd5727;
$green-cool-50: #3e8520;
$gold-50: #8e704f;
$green-warm-50: #6f7a41;
$blue-50: #357ab2;
$violet-warm-60: #864... | 1.0 | Tokens - Add Hub colors - ## Description
These color variables need to be added as tokens:
$red-70v: #8b1303;
$red-60v: #b51d09;
$indigo-cool-60: #3f57a6;
$red-60: #a23737;
$mint-cool-50: #21827f;
$orange-warm-50: #bd5727;
$green-cool-50: #3e8520;
$gold-50: #8e704f;
$green-warm-50: #6f7a41;
$blue-50: #357a... | non_priority | tokens add hub colors description these color variables need to be added as tokens red red indigo cool red mint cool orange warm green cool gold green warm blue violet warm contextual variable names col... | 0 |
113,090 | 24,365,683,380 | IssuesEvent | 2022-10-03 15:00:01 | ClickHouse/ClickHouse | https://api.github.com/repos/ClickHouse/ClickHouse | opened | topK with counts | unfinished code | **Describe the unexpected behaviour**
Similar to #34807, I'd like to query counts for `topK` elements.
I checked the source code and Clickhouse's SpaceSaving algorithm implements both the approximate count and error properties that I'm looking for:
https://github.com/ClickHouse/ClickHouse/blob/bf574b91547aec79936... | 1.0 | topK with counts - **Describe the unexpected behaviour**
Similar to #34807, I'd like to query counts for `topK` elements.
I checked the source code and Clickhouse's SpaceSaving algorithm implements both the approximate count and error properties that I'm looking for:
https://github.com/ClickHouse/ClickHouse/blob/... | non_priority | topk with counts describe the unexpected behaviour similar to i d like to query counts for topk elements i checked the source code and clickhouse s spacesaving algorithm implements both the approximate count and error properties that i m looking for but there is only a query function to return th... | 0 |
276,145 | 20,971,163,349 | IssuesEvent | 2022-03-28 11:30:50 | KubOS-Preservation-Group/kubos | https://api.github.com/repos/KubOS-Preservation-Group/kubos | opened | improvements to the docs build process | documentation help wanted | Currently the docs _do_ build, but its not the most ideal setup. heres some things i'd want to do to make the build process better:
- [ ] I personally think it might be easier to manage if the builds were done by GH actions instead of CircleCI. We should evaluate how much effort it would take to migrate and what the... | 1.0 | improvements to the docs build process - Currently the docs _do_ build, but its not the most ideal setup. heres some things i'd want to do to make the build process better:
- [ ] I personally think it might be easier to manage if the builds were done by GH actions instead of CircleCI. We should evaluate how much eff... | non_priority | improvements to the docs build process currently the docs do build but its not the most ideal setup heres some things i d want to do to make the build process better i personally think it might be easier to manage if the builds were done by gh actions instead of circleci we should evaluate how much effor... | 0 |
45,250 | 23,981,602,914 | IssuesEvent | 2022-09-13 15:27:16 | runtimeverification/haskell-backend | https://api.github.com/repos/runtimeverification/haskell-backend | closed | Performance regression in KEVM proofs | investigation performance | [kevm-slow.tar.gz](https://github.com/kframework/kore/files/5452889/kevm-slow.tar.gz)
The submitted proof still passes, but it runs 4X slower roughly than it did prior to the function-encoding updates.
I'll look at the kore-repl output here and see if some lemmas I expect to be applying are not, but I think it'... | True | Performance regression in KEVM proofs - [kevm-slow.tar.gz](https://github.com/kframework/kore/files/5452889/kevm-slow.tar.gz)
The submitted proof still passes, but it runs 4X slower roughly than it did prior to the function-encoding updates.
I'll look at the kore-repl output here and see if some lemmas I expect... | non_priority | performance regression in kevm proofs the submitted proof still passes but it runs slower roughly than it did prior to the function encoding updates i ll look at the kore repl output here and see if some lemmas i expect to be applying are not but i think it s likely a good idea to also profile the ba... | 0 |
185,262 | 21,785,108,757 | IssuesEvent | 2022-05-14 02:31:39 | iceColdChris/ZodiacWebsite | https://api.github.com/repos/iceColdChris/ZodiacWebsite | closed | CVE-2021-29060 (Medium) detected in color-string-0.3.0.tgz - autoclosed | security vulnerability | ## CVE-2021-29060 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>color-string-0.3.0.tgz</b></p></summary>
<p>Parser and generator for CSS color strings</p>
<p>Library home page: <a ... | True | CVE-2021-29060 (Medium) detected in color-string-0.3.0.tgz - autoclosed - ## CVE-2021-29060 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>color-string-0.3.0.tgz</b></p></summary>
<... | non_priority | cve medium detected in color string tgz autoclosed cve medium severity vulnerability vulnerable library color string tgz parser and generator for css color strings library home page a href path to dependency file package json path to vulnerable library node modul... | 0 |
348,326 | 24,911,324,551 | IssuesEvent | 2022-10-29 22:21:35 | jaamanu/Javascript-Capstone-Project | https://api.github.com/repos/jaamanu/Javascript-Capstone-Project | closed | [4pt] Create feature : add new comment - Student B | documentation | Implement the "add new comment" form on the Comments pop up according to the wireframe:
When the user clicks on the "Comment" button, the data is recorded in the Involvement API and the screen is updated. | 1.0 | [4pt] Create feature : add new comment - Student B - Implement the "add new comment" form on the Comments pop up according to the wireframe:
When the user clicks on the "Comment" button, the data is recorded in the Involvement API and the screen is updated. | non_priority | create feature add new comment student b implement the add new comment form on the comments pop up according to the wireframe when the user clicks on the comment button the data is recorded in the involvement api and the screen is updated | 0 |
1,508 | 6,176,259,620 | IssuesEvent | 2017-07-01 11:52:44 | arduino/Arduino | https://api.github.com/repos/arduino/Arduino | closed | Nano WDT/ResetButton Failure | Architecture: AVR Type: Duplicate | Greetings,
I am developing an interrupt driven I/O intensive program using a Nano that crashes after a few days of continuous operation. I have WDT implemented which does not correct the problem nor does pressing the reset button. A power cycle reset is required to get it running again. When it fails the P13 L... | 1.0 | Nano WDT/ResetButton Failure - Greetings,
I am developing an interrupt driven I/O intensive program using a Nano that crashes after a few days of continuous operation. I have WDT implemented which does not correct the problem nor does pressing the reset button. A power cycle reset is required to get it runnin... | non_priority | nano wdt resetbutton failure greetings i am developing an interrupt driven i o intensive program using a nano that crashes after a few days of continuous operation i have wdt implemented which does not correct the problem nor does pressing the reset button a power cycle reset is required to get it runnin... | 0 |
121,919 | 12,137,229,071 | IssuesEvent | 2020-04-23 15:26:28 | blockstack/docs.blockstack | https://api.github.com/repos/blockstack/docs.blockstack | opened | Add integration design guidance to Connect get started | documentation | https://docs.blockstack.org/develop/connect/get-started.html
Instructions for how developers should include "Get started" and "Sign in" options on their landing pages and not "Sign in with Blockstack", etc. | 1.0 | Add integration design guidance to Connect get started - https://docs.blockstack.org/develop/connect/get-started.html
Instructions for how developers should include "Get started" and "Sign in" options on their landing pages and not "Sign in with Blockstack", etc. | non_priority | add integration design guidance to connect get started instructions for how developers should include get started and sign in options on their landing pages and not sign in with blockstack etc | 0 |
51,857 | 27,274,391,536 | IssuesEvent | 2023-02-23 02:52:12 | ClickHouse/ClickHouse | https://api.github.com/repos/ClickHouse/ClickHouse | opened | Join in materialized view is 60x slower than in select statement. | performance | **Describe the situation**
Seems materialized view with join not working with **FillRightFirst** plan, please loot at the script blew.
Thank you for your time.
Select statement statistics:
`0 rows in set. Elapsed: 0.021 sec. Processed 262.02 thousand rows, 2.10 MB (12.69 million rows/s., 101.50 MB/s.)`
M... | True | Join in materialized view is 60x slower than in select statement. - **Describe the situation**
Seems materialized view with join not working with **FillRightFirst** plan, please loot at the script blew.
Thank you for your time.
Select statement statistics:
`0 rows in set. Elapsed: 0.021 sec. Processed 262.0... | non_priority | join in materialized view is slower than in select statement describe the situation seems materialized view with join not working with fillrightfirst plan please loot at the script blew thank you for your time select statement statistics rows in set elapsed sec processed thous... | 0 |
2,312 | 5,071,321,222 | IssuesEvent | 2016-12-26 12:31:59 | AdguardTeam/AdguardForAndroid | https://api.github.com/repos/AdguardTeam/AdguardForAndroid | opened | net.probki.geonet doesn't work correctly when Adguard is ON | Compatibility | 1475129
Та же проблема, что и в cityguide
Адг блокирует загрузку данных (навигационных карт)
GeoNet https://play.google.com/store/apps/details?id=net.probki.geonet&hl=ru
Мы для этого используем FTP. Вы режете порты которые назначаются клиентам нашими серверами (например 56839, 60182, 52897, 56842 и т.п.).
| True | net.probki.geonet doesn't work correctly when Adguard is ON - 1475129
Та же проблема, что и в cityguide
Адг блокирует загрузку данных (навигационных карт)
GeoNet https://play.google.com/store/apps/details?id=net.probki.geonet&hl=ru
Мы для этого используем FTP. Вы режете порты которые назначаются клиентам нашими с... | non_priority | net probki geonet doesn t work correctly when adguard is on та же проблема что и в cityguide адг блокирует загрузку данных навигационных карт geonet мы для этого используем ftp вы режете порты которые назначаются клиентам нашими серверами например и т п | 0 |
49,352 | 6,023,363,061 | IssuesEvent | 2017-06-07 23:51:07 | etsy/phan | https://api.github.com/repos/etsy/phan | opened | Check if errors in (possibly different) methods of duplicate classes are reported in the correct files and with the correct FQSENs | tests | tests/multi_test would be a good place to add a test for this.
- If this bug is confirmed, see if it's easy to fix it.
When the class is being analyzed, it may be given the wrong alternate FQSEN (may not be well tested)
(E.g. if a method calls an undefined method)
| 1.0 | Check if errors in (possibly different) methods of duplicate classes are reported in the correct files and with the correct FQSENs - tests/multi_test would be a good place to add a test for this.
- If this bug is confirmed, see if it's easy to fix it.
When the class is being analyzed, it may be given the wrong al... | non_priority | check if errors in possibly different methods of duplicate classes are reported in the correct files and with the correct fqsens tests multi test would be a good place to add a test for this if this bug is confirmed see if it s easy to fix it when the class is being analyzed it may be given the wrong al... | 0 |
164,614 | 25,994,799,603 | IssuesEvent | 2022-12-20 10:39:14 | elastic/kibana | https://api.github.com/repos/elastic/kibana | opened | [APM] Rename and restructure components for mobile service details page | Team:APM design | In the first iteration, we hide the components not relevant with mobile - https://github.com/elastic/kibana/issues/143498
we kept the following components which are shared with the other services
1. Latency
2. Throughput
3. Failed Transaction rate
4. Dependencies
5. Transactions table
**Service overview pag... | 1.0 | [APM] Rename and restructure components for mobile service details page - In the first iteration, we hide the components not relevant with mobile - https://github.com/elastic/kibana/issues/143498
we kept the following components which are shared with the other services
1. Latency
2. Throughput
3. Failed Transacti... | non_priority | rename and restructure components for mobile service details page in the first iteration we hide the components not relevant with mobile we kept the following components which are shared with the other services latency throughput failed transaction rate dependencies transactions table ... | 0 |
103,788 | 16,609,469,880 | IssuesEvent | 2021-06-02 09:41:36 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | closed | Vulnerability roundup 100: openvswitch-2.13.0: 1 advisory [7.5] | 1.severity: security | [search](https://search.nix.gsc.io/?q=openvswitch&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=openvswitch+in%3Apath&type=Code)
* [ ] [CVE-2020-35498](https://nvd.nist.gov/vuln/detail/CVE-2020-35498) CVSSv3=7.5 (nixos-20.09)
Scanned versions: nixos-20.09: 12d9950bf47.... | True | Vulnerability roundup 100: openvswitch-2.13.0: 1 advisory [7.5] - [search](https://search.nix.gsc.io/?q=openvswitch&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=openvswitch+in%3Apath&type=Code)
* [ ] [CVE-2020-35498](https://nvd.nist.gov/vuln/detail/CVE-2020-35498) CVS... | non_priority | vulnerability roundup openvswitch advisory nixos scanned versions nixos cc kmcopper cc netixx | 0 |
188,539 | 22,046,608,510 | IssuesEvent | 2022-05-30 02:58:56 | sshivananda/ts-sqs-consumer | https://api.github.com/repos/sshivananda/ts-sqs-consumer | closed | CVE-2012-6708 (Medium) detected in jquery-1.7.2.min.js - autoclosed | security vulnerability | ## CVE-2012-6708 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.7.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="htt... | True | CVE-2012-6708 (Medium) detected in jquery-1.7.2.min.js - autoclosed - ## CVE-2012-6708 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.7.2.min.js</b></p></summary>
<p>JavaSc... | non_priority | cve medium detected in jquery min js autoclosed cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file tmp ws scm ts sqs consumer node modules jmespath index html pat... | 0 |
213,862 | 24,022,473,265 | IssuesEvent | 2022-09-15 08:48:14 | sast-automation-dev/easybuggy4sb-25 | https://api.github.com/repos/sast-automation-dev/easybuggy4sb-25 | opened | google-oauth-client-1.30.3.jar: 4 vulnerabilities (highest severity is: 9.1) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>google-oauth-client-1.30.3.jar</b></p></summary>
<p>Google OAuth Client Library for Java. Functionality that works on all supported Java platforms,
including Java... | True | google-oauth-client-1.30.3.jar: 4 vulnerabilities (highest severity is: 9.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>google-oauth-client-1.30.3.jar</b></p></summary>
<p>Google OAuth Client Library for Jav... | non_priority | google oauth client jar vulnerabilities highest severity is vulnerable library google oauth client jar google oauth client library for java functionality that works on all supported java platforms including java or higher desktop se and web ee android and google app e... | 0 |
14,464 | 3,402,652,293 | IssuesEvent | 2015-12-03 01:15:15 | grpc/grpc | https://api.github.com/repos/grpc/grpc | opened | ruby ext coverage is broken | coverage ruby test | https://grpc-testing.appspot.com/job/gRPC_coverage/956/HTML_Report/
HTTP ERROR 404
Problem accessing /job/gRPC_coverage/956/HTML_Report/ruby_ext_coverage/index.html. Reason:
Not Found
| 1.0 | ruby ext coverage is broken - https://grpc-testing.appspot.com/job/gRPC_coverage/956/HTML_Report/
HTTP ERROR 404
Problem accessing /job/gRPC_coverage/956/HTML_Report/ruby_ext_coverage/index.html. Reason:
Not Found
| non_priority | ruby ext coverage is broken http error problem accessing job grpc coverage html report ruby ext coverage index html reason not found | 0 |
118,577 | 11,983,738,216 | IssuesEvent | 2020-04-07 14:51:52 | softmatterlab/Braph-2.0-Matlab | https://api.github.com/repos/softmatterlab/Braph-2.0-Matlab | closed | Document getAvailableSettings in In- Out-GlobalEfficiency | documentation measure | Document getAvailableSettings() in
- [x] InGlobalEfficiency
- [x] OutGlobalEfficiency
- [x] GlobalEfficiency | 1.0 | Document getAvailableSettings in In- Out-GlobalEfficiency - Document getAvailableSettings() in
- [x] InGlobalEfficiency
- [x] OutGlobalEfficiency
- [x] GlobalEfficiency | non_priority | document getavailablesettings in in out globalefficiency document getavailablesettings in inglobalefficiency outglobalefficiency globalefficiency | 0 |
86,962 | 15,755,910,584 | IssuesEvent | 2021-03-31 02:35:54 | SmartBear/ready-jira-plugin | https://api.github.com/repos/SmartBear/ready-jira-plugin | opened | CVE-2016-1000345 (Medium) detected in bcprov-jdk14-138.jar | security vulnerability | ## CVE-2016-1000345 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcprov-jdk14-138.jar</b></p></summary>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptograph... | True | CVE-2016-1000345 (Medium) detected in bcprov-jdk14-138.jar - ## CVE-2016-1000345 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcprov-jdk14-138.jar</b></p></summary>
<p>The Bouncy ... | non_priority | cve medium detected in bcprov jar cve medium severity vulnerability vulnerable library bcprov jar the bouncy castle crypto package is a java implementation of cryptographic algorithms the package is organised so that it contains a light weight api suitable for use in any environmen... | 0 |
97,805 | 28,505,535,589 | IssuesEvent | 2023-04-18 21:02:57 | sile-typesetter/sile | https://api.github.com/repos/sile-typesetter/sile | closed | v0.14.9 release checklist | builds & releases | - [x] Shuffle any issues being put off to future milestones
- [x] Close all issues in current milestone (except this one)
- [x] Spring clean
- [x] Re-fetch tooling
- [x] Configure and build
- [x] Pass all tests
- [x] Remote CI
- [x] Local
- [x] Cut release
- [x] Push release commit & tag to master
... | 1.0 | v0.14.9 release checklist - - [x] Shuffle any issues being put off to future milestones
- [x] Close all issues in current milestone (except this one)
- [x] Spring clean
- [x] Re-fetch tooling
- [x] Configure and build
- [x] Pass all tests
- [x] Remote CI
- [x] Local
- [x] Cut release
- [x] Push rel... | non_priority | release checklist shuffle any issues being put off to future milestones close all issues in current milestone except this one spring clean re fetch tooling configure and build pass all tests remote ci local cut release push release commit tag to m... | 0 |
246,130 | 20,824,486,788 | IssuesEvent | 2022-03-18 19:00:22 | ChainSafe/ui-monorepo | https://api.github.com/repos/ChainSafe/ui-monorepo | opened | Add ui test coverage for file copying to share folder | Testing | As described, automate the below scenarios:
- User can share a file to a new shared folder and delete original file
- User can share a file to a new shared folder and keep original file
- User can share a file to existing shared folder and delete original file
- User can share a file to existing shared folder an... | 1.0 | Add ui test coverage for file copying to share folder - As described, automate the below scenarios:
- User can share a file to a new shared folder and delete original file
- User can share a file to a new shared folder and keep original file
- User can share a file to existing shared folder and delete original fi... | non_priority | add ui test coverage for file copying to share folder as described automate the below scenarios user can share a file to a new shared folder and delete original file user can share a file to a new shared folder and keep original file user can share a file to existing shared folder and delete original fi... | 0 |
138,138 | 20,360,000,367 | IssuesEvent | 2022-02-20 14:50:13 | plotn/coolreader | https://api.github.com/repos/plotn/coolreader | opened | Убрать непонятное сообщение, появляющееся при старте приложения | system design | Нужно принимать решение за пользователя. Никто, впервые открывший приложение, не поймёт, о чём это.
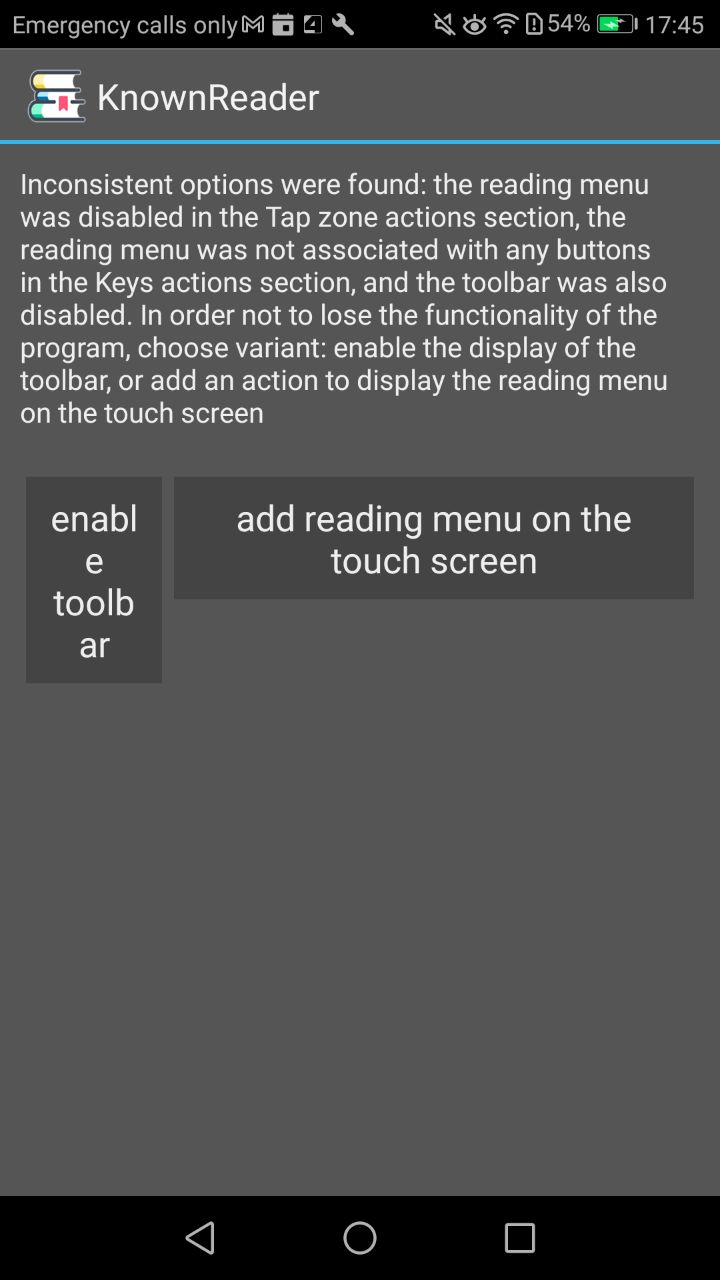
| 1.0 | Убрать непонятное сообщение, появляющееся при старте приложения - Нужно принимать решение за пользователя. Никто, впервые открывший приложение, не поймёт, о чём это.
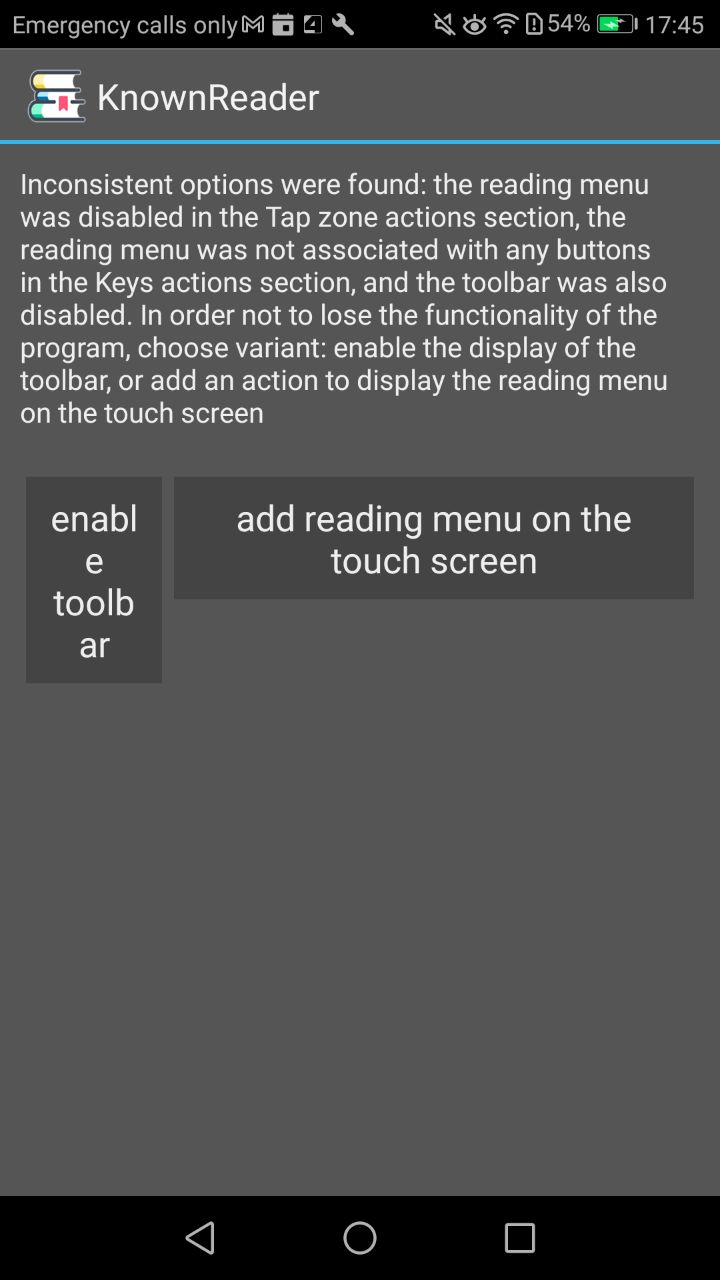
| non_priority | убрать непонятное сообщение появляющееся при старте приложения нужно принимать решение за пользователя никто впервые открывший приложение не поймёт о чём это | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.