Unnamed: 0 int64 1 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 7 112 | repo_url stringlengths 36 141 | action stringclasses 3 values | title stringlengths 3 438 | labels stringlengths 4 308 | body stringlengths 7 254k | index stringclasses 7 values | text_combine stringlengths 96 254k | label stringclasses 2 values | text stringlengths 96 246k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
3,156 | 12,197,547,928 | IssuesEvent | 2020-04-29 20:58:51 | short-d/short | https://api.github.com/repos/short-d/short | opened | [REFACTOR] [UI] $content-width SCSS variable not sensible for all screen sizes | good first issue maintainability | **What is frustrating you?**
The `$content-width` SCSS variable, found in `frontend/src/component/styles/dimension.scss` is set to `1200px` currently, which works for desktop, but does not make sense for mobile. Components affected are: `Header`, `Footer` (but it looks fine since it's centered and just text), `Section`, and `UserShortLinksSection`.
**Your solution**
Refactor so that the `$content-width` variable's value is calculated from the current screen width.
**Screenshots**
iPhone X/XS screen dimensions for example:

| True | [REFACTOR] [UI] $content-width SCSS variable not sensible for all screen sizes - **What is frustrating you?**
The `$content-width` SCSS variable, found in `frontend/src/component/styles/dimension.scss` is set to `1200px` currently, which works for desktop, but does not make sense for mobile. Components affected are: `Header`, `Footer` (but it looks fine since it's centered and just text), `Section`, and `UserShortLinksSection`.
**Your solution**
Refactor so that the `$content-width` variable's value is calculated from the current screen width.
**Screenshots**
iPhone X/XS screen dimensions for example:

| main | content width scss variable not sensible for all screen sizes what is frustrating you the content width scss variable found in frontend src component styles dimension scss is set to currently which works for desktop but does not make sense for mobile components affected are header footer but it looks fine since it s centered and just text section and usershortlinkssection your solution refactor so that the content width variable s value is calculated from the current screen width screenshots iphone x xs screen dimensions for example | 1 |
176,998 | 6,572,534,937 | IssuesEvent | 2017-09-11 03:05:45 | RogueException/Discord.Net | https://api.github.com/repos/RogueException/Discord.Net | closed | Channel Categories are not supported at the API-level | bug priority: critical | In Discord.Net 1.0.1 and on the latest dev(479361bbea4f7baebbb55ceb211ce9f02368b91e), Trying to interact with the bot will fail for any server with categories. Interaction in PMs and in servers without categories works fine.
(Oddly this isn't an issue for my bots still running on 0.9)
Here's a piece of my log from typing and sending a message in one such server:
```[23:47:14.2318847] [Gateway] Received Dispatch (TYPING_START)
[23:47:14.2318847] [Gateway] Unsynced Guild (TYPING_START Guild=63296437932273664).
[23:47:17.8300030] [Gateway] Received Dispatch (MESSAGE_CREATE)
[23:47:17.8305033] [Gateway] Unsynced Guild (MESSAGE_CREATE Guild=63296437932273664).
```
So I decided to do some debugging, and put a breakpoint in `client.MessageReceived`, I got a hit for DM, and for a server without categories, but not for messaging in any channel in a category server. | 1.0 | Channel Categories are not supported at the API-level - In Discord.Net 1.0.1 and on the latest dev(479361bbea4f7baebbb55ceb211ce9f02368b91e), Trying to interact with the bot will fail for any server with categories. Interaction in PMs and in servers without categories works fine.
(Oddly this isn't an issue for my bots still running on 0.9)
Here's a piece of my log from typing and sending a message in one such server:
```[23:47:14.2318847] [Gateway] Received Dispatch (TYPING_START)
[23:47:14.2318847] [Gateway] Unsynced Guild (TYPING_START Guild=63296437932273664).
[23:47:17.8300030] [Gateway] Received Dispatch (MESSAGE_CREATE)
[23:47:17.8305033] [Gateway] Unsynced Guild (MESSAGE_CREATE Guild=63296437932273664).
```
So I decided to do some debugging, and put a breakpoint in `client.MessageReceived`, I got a hit for DM, and for a server without categories, but not for messaging in any channel in a category server. | non_main | channel categories are not supported at the api level in discord net and on the latest dev trying to interact with the bot will fail for any server with categories interaction in pms and in servers without categories works fine oddly this isn t an issue for my bots still running on here s a piece of my log from typing and sending a message in one such server received dispatch typing start unsynced guild typing start guild received dispatch message create unsynced guild message create guild so i decided to do some debugging and put a breakpoint in client messagereceived i got a hit for dm and for a server without categories but not for messaging in any channel in a category server | 0 |
46,079 | 6,007,493,464 | IssuesEvent | 2017-06-06 03:37:35 | Automattic/wp-calypso | https://api.github.com/repos/Automattic/wp-calypso | opened | Publicize: Allow user to specific featured image to use when sharing to different platforms | Editor Media Plans Sharing [Status] Needs Design Review [Type] Enhancement | We should give people the ability to (optionally) manually select an image to be shared to each platform (e.g. force what is output in the `og:image` and `twitter:image` meta tags) when using Publicize (or manual sharing buttons) and to see them in the SEO preview (on Business plans).
#### Steps to reproduce
1. Connect Facebook and Twitter, enable Publicize
2. Create a post with some images in it
3. Publish said post
4. Observe that an image was shared to Facebook/Twitter with your post; if you used a Featured image then that one would have been used, if not then one would have been picked from your main content.
We could possibly add some UI into the editor drawer to allow you to pick an image against each connected service?
<img width="287" alt="screen shot 2017-06-05 at 9 26 31 pm" src="https://cloud.githubusercontent.com/assets/108942/26812576/c4465730-4a35-11e7-8f64-77ffb4c361db.png">
Or alternatively, just offer the ability to upload a different image directly within the SEO preview:
<img width="886" alt="screen_shot_2017-06-05_at_9_35_02_pm" src="https://cloud.githubusercontent.com/assets/108942/26812777/f6df6910-4a36-11e7-9cae-1a7ee64c7011.png"> | 1.0 | Publicize: Allow user to specific featured image to use when sharing to different platforms - We should give people the ability to (optionally) manually select an image to be shared to each platform (e.g. force what is output in the `og:image` and `twitter:image` meta tags) when using Publicize (or manual sharing buttons) and to see them in the SEO preview (on Business plans).
#### Steps to reproduce
1. Connect Facebook and Twitter, enable Publicize
2. Create a post with some images in it
3. Publish said post
4. Observe that an image was shared to Facebook/Twitter with your post; if you used a Featured image then that one would have been used, if not then one would have been picked from your main content.
We could possibly add some UI into the editor drawer to allow you to pick an image against each connected service?
<img width="287" alt="screen shot 2017-06-05 at 9 26 31 pm" src="https://cloud.githubusercontent.com/assets/108942/26812576/c4465730-4a35-11e7-8f64-77ffb4c361db.png">
Or alternatively, just offer the ability to upload a different image directly within the SEO preview:
<img width="886" alt="screen_shot_2017-06-05_at_9_35_02_pm" src="https://cloud.githubusercontent.com/assets/108942/26812777/f6df6910-4a36-11e7-9cae-1a7ee64c7011.png"> | non_main | publicize allow user to specific featured image to use when sharing to different platforms we should give people the ability to optionally manually select an image to be shared to each platform e g force what is output in the og image and twitter image meta tags when using publicize or manual sharing buttons and to see them in the seo preview on business plans steps to reproduce connect facebook and twitter enable publicize create a post with some images in it publish said post observe that an image was shared to facebook twitter with your post if you used a featured image then that one would have been used if not then one would have been picked from your main content we could possibly add some ui into the editor drawer to allow you to pick an image against each connected service img width alt screen shot at pm src or alternatively just offer the ability to upload a different image directly within the seo preview img width alt screen shot at pm src | 0 |
169,240 | 13,131,095,540 | IssuesEvent | 2020-08-06 16:24:26 | HEPCloud/decisionengine | https://api.github.com/repos/HEPCloud/decisionengine | closed | log_level issues in new decisionengine 1.2.0-1 | fixed_in_rc prj_testing | I am trying to test the new functionality which was implemented for issue !84.
The logger section of the /etc/decisionengine/decision_engine.conf is below
'logger' : {'log_file': '/var/log/decisionengine/decision_engine_log',
'max_file_size': 200*1000000,
'max_backup_count': 6,
'log_level': "DEBUG",
},
But although I am running seven channels I do not see any DEBUG entries in any of the logs.
Is any further configuration necessary?
Also what is the syntax to set the log level on a channel by channel basis.
This is set up on fermicloud117.fnal.gov right now, I can give root login if needed.
Steve Timm
| 1.0 | log_level issues in new decisionengine 1.2.0-1 - I am trying to test the new functionality which was implemented for issue !84.
The logger section of the /etc/decisionengine/decision_engine.conf is below
'logger' : {'log_file': '/var/log/decisionengine/decision_engine_log',
'max_file_size': 200*1000000,
'max_backup_count': 6,
'log_level': "DEBUG",
},
But although I am running seven channels I do not see any DEBUG entries in any of the logs.
Is any further configuration necessary?
Also what is the syntax to set the log level on a channel by channel basis.
This is set up on fermicloud117.fnal.gov right now, I can give root login if needed.
Steve Timm
| non_main | log level issues in new decisionengine i am trying to test the new functionality which was implemented for issue the logger section of the etc decisionengine decision engine conf is below logger log file var log decisionengine decision engine log max file size max backup count log level debug but although i am running seven channels i do not see any debug entries in any of the logs is any further configuration necessary also what is the syntax to set the log level on a channel by channel basis this is set up on fnal gov right now i can give root login if needed steve timm | 0 |
489,397 | 14,105,773,908 | IssuesEvent | 2020-11-06 14:00:13 | exc-asia-and-europe/ecpo-annotator | https://api.github.com/repos/exc-asia-and-europe/ecpo-annotator | closed | boxes move positions | bug high priority | In GitLab by @MatthiasArnold on Jul 29, 2019, 22:20
die boxen verschieben sich nach dem speichen immer ein wenig, meist ein paar pixel nach unten.
da wir zum trainieren der neuronalen netzwerke sehr genau sein müssen und die trennlinien ausschliessen müssen, dass sie gerade NICHT trainiert werden, ist das schlecht. | 1.0 | boxes move positions - In GitLab by @MatthiasArnold on Jul 29, 2019, 22:20
die boxen verschieben sich nach dem speichen immer ein wenig, meist ein paar pixel nach unten.
da wir zum trainieren der neuronalen netzwerke sehr genau sein müssen und die trennlinien ausschliessen müssen, dass sie gerade NICHT trainiert werden, ist das schlecht. | non_main | boxes move positions in gitlab by matthiasarnold on jul die boxen verschieben sich nach dem speichen immer ein wenig meist ein paar pixel nach unten da wir zum trainieren der neuronalen netzwerke sehr genau sein müssen und die trennlinien ausschliessen müssen dass sie gerade nicht trainiert werden ist das schlecht | 0 |
5,474 | 27,356,764,984 | IssuesEvent | 2023-02-27 13:23:25 | centerofci/mathesar | https://api.github.com/repos/centerofci/mathesar | closed | Wait until server is ready after upgrade to reload page | type: bug work: frontend status: ready restricted: maintainers | Reported by @dmos62:
The service layer container takes time to restart after upgrade. The frontend reloads page as soon as upgrade request completes, this causes the page to display a 502.
We need to wait until the service is ready before reloading the page.
| True | Wait until server is ready after upgrade to reload page - Reported by @dmos62:
The service layer container takes time to restart after upgrade. The frontend reloads page as soon as upgrade request completes, this causes the page to display a 502.
We need to wait until the service is ready before reloading the page.
| main | wait until server is ready after upgrade to reload page reported by the service layer container takes time to restart after upgrade the frontend reloads page as soon as upgrade request completes this causes the page to display a we need to wait until the service is ready before reloading the page | 1 |
2,645 | 9,036,410,186 | IssuesEvent | 2019-02-09 00:10:04 | dgets/lasttime | https://api.github.com/repos/dgets/lasttime | closed | Create the wiki | enhancement maintainability | This project has had versions up for release at this point, and it's gotten a little bit of attention, at least on Diaspora. This means that people could be coming along and wanting to take a look at the capabilities and screenshots of the application, as well as a general synopsis. Get this information into the wiki so that people can find the documentation that they may be looking for. | True | Create the wiki - This project has had versions up for release at this point, and it's gotten a little bit of attention, at least on Diaspora. This means that people could be coming along and wanting to take a look at the capabilities and screenshots of the application, as well as a general synopsis. Get this information into the wiki so that people can find the documentation that they may be looking for. | main | create the wiki this project has had versions up for release at this point and it s gotten a little bit of attention at least on diaspora this means that people could be coming along and wanting to take a look at the capabilities and screenshots of the application as well as a general synopsis get this information into the wiki so that people can find the documentation that they may be looking for | 1 |
306,677 | 23,169,036,445 | IssuesEvent | 2022-07-30 12:12:28 | mlabs-haskell/ply | https://api.github.com/repos/mlabs-haskell/ply | closed | Update `example` post `staging` changes | documentation help wanted | The `example` in `staging` branch needs to be updated. It is also a good place to showcase how to utilize the newly added `new-ledger-namespace` flag to unify `ply` usage across offchain and onchain.
It also implies more nix pain. | 1.0 | Update `example` post `staging` changes - The `example` in `staging` branch needs to be updated. It is also a good place to showcase how to utilize the newly added `new-ledger-namespace` flag to unify `ply` usage across offchain and onchain.
It also implies more nix pain. | non_main | update example post staging changes the example in staging branch needs to be updated it is also a good place to showcase how to utilize the newly added new ledger namespace flag to unify ply usage across offchain and onchain it also implies more nix pain | 0 |
576,853 | 17,096,586,938 | IssuesEvent | 2021-07-09 04:15:50 | rafinkanisa/ngm-reportDesk | https://api.github.com/repos/rafinkanisa/ngm-reportDesk | opened | RH ET ESNFI Program Coordinating Partners | priority | It was requested to altered the "Programme Partners" to "Program Coordinating Partners" in Project Plan page.
The following should also be added to the list of program coordinating partners :
RRF/IOM, SWAN, UNHCR, IOM, CWW, CCM, Christian Aid, ERM/IRC, IRC, CRS
Alter the name to all associated with it (including the header title in the data download). Implement this only to ESNFI Cluster in Ethiopia. | 1.0 | RH ET ESNFI Program Coordinating Partners - It was requested to altered the "Programme Partners" to "Program Coordinating Partners" in Project Plan page.
The following should also be added to the list of program coordinating partners :
RRF/IOM, SWAN, UNHCR, IOM, CWW, CCM, Christian Aid, ERM/IRC, IRC, CRS
Alter the name to all associated with it (including the header title in the data download). Implement this only to ESNFI Cluster in Ethiopia. | non_main | rh et esnfi program coordinating partners it was requested to altered the programme partners to program coordinating partners in project plan page the following should also be added to the list of program coordinating partners rrf iom swan unhcr iom cww ccm christian aid erm irc irc crs alter the name to all associated with it including the header title in the data download implement this only to esnfi cluster in ethiopia | 0 |
189,312 | 22,047,015,988 | IssuesEvent | 2022-05-30 03:43:04 | panasalap/linux-4.19.72_test1 | https://api.github.com/repos/panasalap/linux-4.19.72_test1 | closed | WS-2021-0333 (Medium) detected in linux-yoctov5.4.51 - autoclosed | security vulnerability | ## WS-2021-0333 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in HEAD commit: <a href="https://github.com/panasalap/linux-4.19.72/commit/f1b7c617b9b8f4135ab2f75a0c407cc44d43683f">f1b7c617b9b8f4135ab2f75a0c407cc44d43683f</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/nfc/llcp_sock.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/nfc/llcp_sock.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Linux Kernel in versions from v5.4.112 to before v5.4.119 contains a use-after-free vulnerability at llcp_sock_bind/connect.
<p>Publish Date: 2021-05-31
<p>URL: <a href=https://github.com/gregkh/linux/commit/e32352070bcac22be6ed8ab635debc280bb65b8c>WS-2021-0333</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://osv.dev/vulnerability/UVI-2021-1000440/">https://osv.dev/vulnerability/UVI-2021-1000440/</a></p>
<p>Release Date: 2021-05-31</p>
<p>Fix Resolution: v5.4.119</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2021-0333 (Medium) detected in linux-yoctov5.4.51 - autoclosed - ## WS-2021-0333 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in HEAD commit: <a href="https://github.com/panasalap/linux-4.19.72/commit/f1b7c617b9b8f4135ab2f75a0c407cc44d43683f">f1b7c617b9b8f4135ab2f75a0c407cc44d43683f</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/nfc/llcp_sock.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/nfc/llcp_sock.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Linux Kernel in versions from v5.4.112 to before v5.4.119 contains a use-after-free vulnerability at llcp_sock_bind/connect.
<p>Publish Date: 2021-05-31
<p>URL: <a href=https://github.com/gregkh/linux/commit/e32352070bcac22be6ed8ab635debc280bb65b8c>WS-2021-0333</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://osv.dev/vulnerability/UVI-2021-1000440/">https://osv.dev/vulnerability/UVI-2021-1000440/</a></p>
<p>Release Date: 2021-05-31</p>
<p>Fix Resolution: v5.4.119</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_main | ws medium detected in linux autoclosed ws medium severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in head commit a href found in base branch master vulnerable source files net nfc llcp sock c net nfc llcp sock c vulnerability details linux kernel in versions from to before contains a use after free vulnerability at llcp sock bind connect publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
5,831 | 30,862,404,215 | IssuesEvent | 2023-08-03 05:00:14 | rdmorganiser/rdmo | https://api.github.com/repos/rdmorganiser/rdmo | closed | Switch from PyUp to Dependabot | type: feature request type: maintainance | Hi there. The feature request issue template was not that fitting, but this is not a bug report either.
### Rationale / Begründung
I saw that you have a .pyup.yml in you repo, but the requirements.txt has not been touchend by the PyUp since 2020. I guess PyUp switched to a paid business model.
Would you like to have dependency updates done with GitHub's Dependabot? I could submit a PR, if you like.
### Affected
Dependency updates.
### Minimal functionality
Working dependency updates.
### Nice-to-have functionality
not applicable
### References / Verweise
- https://docs.github.com/en/code-security/dependabot/working-with-dependabot
| True | Switch from PyUp to Dependabot - Hi there. The feature request issue template was not that fitting, but this is not a bug report either.
### Rationale / Begründung
I saw that you have a .pyup.yml in you repo, but the requirements.txt has not been touchend by the PyUp since 2020. I guess PyUp switched to a paid business model.
Would you like to have dependency updates done with GitHub's Dependabot? I could submit a PR, if you like.
### Affected
Dependency updates.
### Minimal functionality
Working dependency updates.
### Nice-to-have functionality
not applicable
### References / Verweise
- https://docs.github.com/en/code-security/dependabot/working-with-dependabot
| main | switch from pyup to dependabot hi there the feature request issue template was not that fitting but this is not a bug report either rationale begründung i saw that you have a pyup yml in you repo but the requirements txt has not been touchend by the pyup since i guess pyup switched to a paid business model would you like to have dependency updates done with github s dependabot i could submit a pr if you like affected dependency updates minimal functionality working dependency updates nice to have functionality not applicable references verweise | 1 |
797 | 4,413,777,166 | IssuesEvent | 2016-08-13 02:01:25 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | Synchronize module do not expand ansible_ssh_private_key_file variable | bug_report waiting_on_maintainer | ##### Issue Type:
- Bug Report
##### Component Name:
synchronize module
##### Ansible Version:
```
ansible 2.0.1.0
config file = /home/david/gitbi/lifemall/ansible/ansible.cfg
configured module search path = Default w/o overrides
```
##### Ansible Configuration:
(nothing)
##### Environment:
Ubuntu 15.10
##### Summary:
Origin : https://github.com/ansible/ansible/issues/15015
I am using variable in ansible_ssh_private_key_file variable and the module do not "render" it in order to have a constant string. E.g. "{{ playbook_dir }}/some/path" is not rendered to "/playbook/path/some/path"
##### Steps To Reproduce:
Set ansible_ssh_private_key_file to some content with variables
Use synchronize module ... It fail.
Then hack:
```
- name: Make synchronize works
set_fact:
ansible_ssh_private_key_file: '{{ ansible_ssh_private_key_file }}'
- name: Go!
synchronize: ...
```
##### Expected Results:
It works!
##### Actual Results:
```
fatal: [server]: FAILED! => {"changed": false, "cmd": "/usr/bin/rsync --delay-updates -F --compress --delete-after --archive --rsh '/usr/bin/ssh -i {{ environment_directory }}/ssh/keys/local_rsa -S none -o StrictHostKeyChecking=no' --rsync-path=\"sudo rsync\" --out-format='<<CHANGED>>%i %n%L' \"/home/david/project/\" \"vagrant@192.168.56.4:/var/www/project/test/source/\"", "failed": true, "msg": "Warning: Identity file {{ not accessible: No such file or directory.\nssh: Could not resolve hostname environment_directory: Name or service not known\r\nrsync: connection unexpectedly closed (0 bytes received so far) [sender]\nrsync error: unexplained error (code 255) at io.c(226) [sender=3.1.1]\n", "rc": 255}
``` | True | Synchronize module do not expand ansible_ssh_private_key_file variable - ##### Issue Type:
- Bug Report
##### Component Name:
synchronize module
##### Ansible Version:
```
ansible 2.0.1.0
config file = /home/david/gitbi/lifemall/ansible/ansible.cfg
configured module search path = Default w/o overrides
```
##### Ansible Configuration:
(nothing)
##### Environment:
Ubuntu 15.10
##### Summary:
Origin : https://github.com/ansible/ansible/issues/15015
I am using variable in ansible_ssh_private_key_file variable and the module do not "render" it in order to have a constant string. E.g. "{{ playbook_dir }}/some/path" is not rendered to "/playbook/path/some/path"
##### Steps To Reproduce:
Set ansible_ssh_private_key_file to some content with variables
Use synchronize module ... It fail.
Then hack:
```
- name: Make synchronize works
set_fact:
ansible_ssh_private_key_file: '{{ ansible_ssh_private_key_file }}'
- name: Go!
synchronize: ...
```
##### Expected Results:
It works!
##### Actual Results:
```
fatal: [server]: FAILED! => {"changed": false, "cmd": "/usr/bin/rsync --delay-updates -F --compress --delete-after --archive --rsh '/usr/bin/ssh -i {{ environment_directory }}/ssh/keys/local_rsa -S none -o StrictHostKeyChecking=no' --rsync-path=\"sudo rsync\" --out-format='<<CHANGED>>%i %n%L' \"/home/david/project/\" \"vagrant@192.168.56.4:/var/www/project/test/source/\"", "failed": true, "msg": "Warning: Identity file {{ not accessible: No such file or directory.\nssh: Could not resolve hostname environment_directory: Name or service not known\r\nrsync: connection unexpectedly closed (0 bytes received so far) [sender]\nrsync error: unexplained error (code 255) at io.c(226) [sender=3.1.1]\n", "rc": 255}
``` | main | synchronize module do not expand ansible ssh private key file variable issue type bug report component name synchronize module ansible version ansible config file home david gitbi lifemall ansible ansible cfg configured module search path default w o overrides ansible configuration nothing environment ubuntu summary origin i am using variable in ansible ssh private key file variable and the module do not render it in order to have a constant string e g playbook dir some path is not rendered to playbook path some path steps to reproduce set ansible ssh private key file to some content with variables use synchronize module it fail then hack name make synchronize works set fact ansible ssh private key file ansible ssh private key file name go synchronize expected results it works actual results fatal failed changed false cmd usr bin rsync delay updates f compress delete after archive rsh usr bin ssh i environment directory ssh keys local rsa s none o stricthostkeychecking no rsync path sudo rsync out format i n l home david project vagrant var www project test source failed true msg warning identity file not accessible no such file or directory nssh could not resolve hostname environment directory name or service not known r nrsync connection unexpectedly closed bytes received so far nrsync error unexplained error code at io c n rc | 1 |
18,470 | 24,550,399,309 | IssuesEvent | 2022-10-12 12:10:23 | bazelbuild/bazel | https://api.github.com/repos/bazelbuild/bazel | closed | Documentation issue: Installing Bazel on Ubuntu | P4 more data needed type: support / not a bug (process) team-OSS | Documentation URL: https://docs.bazel.build/versions/4.0.0/install-ubuntu.html
I had to install tensorflow, but it had error. ubuntu version: ubuntu-18.04-desktop-amd64.iso
Uncompressing..error [./bazel-2.0.0-installer-linux-x86_64.sh]: missing 1232 bytes in zipfile
(attempting to process anyway)
error: invalid zip file with overlapped components (possible zip bomb)
| 1.0 | Documentation issue: Installing Bazel on Ubuntu - Documentation URL: https://docs.bazel.build/versions/4.0.0/install-ubuntu.html
I had to install tensorflow, but it had error. ubuntu version: ubuntu-18.04-desktop-amd64.iso
Uncompressing..error [./bazel-2.0.0-installer-linux-x86_64.sh]: missing 1232 bytes in zipfile
(attempting to process anyway)
error: invalid zip file with overlapped components (possible zip bomb)
| non_main | documentation issue installing bazel on ubuntu documentation url i had to install tensorflow but it had error ubuntu version ubuntu desktop iso uncompressing error missing bytes in zipfile attempting to process anyway error invalid zip file with overlapped components possible zip bomb | 0 |
2,533 | 8,657,431,119 | IssuesEvent | 2018-11-27 21:18:31 | Kapeli/Dash-User-Contributions | https://api.github.com/repos/Kapeli/Dash-User-Contributions | closed | Flux Docset maintainer needed | needs maintainer | I can no longer have time to maintain this docset and I am looking for additional contributors to assist. My repo is located at https://github.com/epitaphmike/flux-dash. If this is something you are interested in helping with please reach out. Thank you.
| True | Flux Docset maintainer needed - I can no longer have time to maintain this docset and I am looking for additional contributors to assist. My repo is located at https://github.com/epitaphmike/flux-dash. If this is something you are interested in helping with please reach out. Thank you.
| main | flux docset maintainer needed i can no longer have time to maintain this docset and i am looking for additional contributors to assist my repo is located at if this is something you are interested in helping with please reach out thank you | 1 |
991 | 4,756,700,629 | IssuesEvent | 2016-10-24 14:42:02 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | Expose replace module's backup file path | affects_1.8 feature_idea waiting_on_maintainer | ##### Issue Type:
Feature Idea
##### Ansible Version:
1.8
##### Environment:
N/A
##### Summary:
Expose backup file path in the output of replace module.
##### Steps To Reproduce:
N/A
##### Expected Results:
We would add "backup" and the file path to the JSON output.
##### Actual Results:
N/A
| True | Expose replace module's backup file path - ##### Issue Type:
Feature Idea
##### Ansible Version:
1.8
##### Environment:
N/A
##### Summary:
Expose backup file path in the output of replace module.
##### Steps To Reproduce:
N/A
##### Expected Results:
We would add "backup" and the file path to the JSON output.
##### Actual Results:
N/A
| main | expose replace module s backup file path issue type feature idea ansible version environment n a summary expose backup file path in the output of replace module steps to reproduce n a expected results we would add backup and the file path to the json output actual results n a | 1 |
5,256 | 26,601,326,669 | IssuesEvent | 2023-01-23 15:58:29 | centerofci/mathesar | https://api.github.com/repos/centerofci/mathesar | closed | Delete icon for new records | type: enhancement work: frontend status: ready restricted: maintainers | Figma:
<img width="301" alt="Screenshot 2023-01-20 at 6 56 36 PM" src="https://user-images.githubusercontent.com/11032856/213705651-2399951c-5175-4d19-ac4f-8b5db5e4e223.png">
| True | Delete icon for new records - Figma:
<img width="301" alt="Screenshot 2023-01-20 at 6 56 36 PM" src="https://user-images.githubusercontent.com/11032856/213705651-2399951c-5175-4d19-ac4f-8b5db5e4e223.png">
| main | delete icon for new records figma img width alt screenshot at pm src | 1 |
4,893 | 25,124,617,167 | IssuesEvent | 2022-11-09 10:44:41 | rthadur/bazel | https://api.github.com/repos/rthadur/bazel | closed | Test for Bazel_IO | awaiting-review awaiting-user-response awaiting-PR-merge awaiting-maintainer | ### Description
test
### Issue Type
_No response_
### Operating System
_No response_
### Coral Device
_No response_
### Other Devices
_No response_
### Programming Language
_No response_
### Relevant Log Output
_No response_ | True | Test for Bazel_IO - ### Description
test
### Issue Type
_No response_
### Operating System
_No response_
### Coral Device
_No response_
### Other Devices
_No response_
### Programming Language
_No response_
### Relevant Log Output
_No response_ | main | test for bazel io description test issue type no response operating system no response coral device no response other devices no response programming language no response relevant log output no response | 1 |
1,261 | 5,350,481,546 | IssuesEvent | 2017-02-19 02:21:35 | gogits/gogs | https://api.github.com/repos/gogits/gogs | closed | Protected branch | kind/feature status/assigned to maintainer status/needs feedback | Reference https://about.gitlab.com/2014/09/29/gitlab-flow/
Reference https://code.google.com/p/gerrit/
Gogs should have a feature of protected branch. Let say `master` is a protected branch, then:
- Nobody can push directly to `master`
- Everybody\* can checkout/fork from `master`
- Everybody\* submit a merge request / code review request for his/her new branch (features/fixes)
- Everybody\* can comment/discuss the diff, preferable line-by-line
- Only those with "Reviewer" or "Supervisor" or "Senior" privilege can vote up/down on a merge request / code review
- A merge request can only be eligible to be merged to master when having at least [a number] 2 of up votes. This parameter should be defined in a config file, environment variable, or runtime argument, so that nobody, even master or supreme admin can bypass code review process by setting it to 1 and self-review their code.
*Everybody is any user with sufficient authorization to read a project `master` and write to their own name space.
| True | Protected branch - Reference https://about.gitlab.com/2014/09/29/gitlab-flow/
Reference https://code.google.com/p/gerrit/
Gogs should have a feature of protected branch. Let say `master` is a protected branch, then:
- Nobody can push directly to `master`
- Everybody\* can checkout/fork from `master`
- Everybody\* submit a merge request / code review request for his/her new branch (features/fixes)
- Everybody\* can comment/discuss the diff, preferable line-by-line
- Only those with "Reviewer" or "Supervisor" or "Senior" privilege can vote up/down on a merge request / code review
- A merge request can only be eligible to be merged to master when having at least [a number] 2 of up votes. This parameter should be defined in a config file, environment variable, or runtime argument, so that nobody, even master or supreme admin can bypass code review process by setting it to 1 and self-review their code.
*Everybody is any user with sufficient authorization to read a project `master` and write to their own name space.
| main | protected branch reference reference gogs should have a feature of protected branch let say master is a protected branch then nobody can push directly to master everybody can checkout fork from master everybody submit a merge request code review request for his her new branch features fixes everybody can comment discuss the diff preferable line by line only those with reviewer or supervisor or senior privilege can vote up down on a merge request code review a merge request can only be eligible to be merged to master when having at least of up votes this parameter should be defined in a config file environment variable or runtime argument so that nobody even master or supreme admin can bypass code review process by setting it to and self review their code everybody is any user with sufficient authorization to read a project master and write to their own name space | 1 |
135,143 | 5,243,005,617 | IssuesEvent | 2017-01-31 19:32:36 | pytorch/pytorch | https://api.github.com/repos/pytorch/pytorch | closed | undefined symbol: sormqr_ | dependency bug high priority | I compiled `pytorch` (using both Python 2 and Python 3) with CUDA support on Ubuntu 16.04 having gcc 4.8.5. The install process terminated with no critical errors.
Torch is already installed on the same machine and works fine.
When importing `pytorch` I get the following error:
----> 1 import torch
/home/tudor/anaconda2/lib/python2.7/site-packages/torch/__init__.pyc in <module>()
43 sys.setdlopenflags(_dl_flags.RTLD_GLOBAL | _dl_flags.RTLD_NOW)
44
---> 45 from torch._C import *
46
47 __all__ += [name for name in dir(_C)
ImportError: /home/tudor/anaconda2/lib/python2.7/site-packages/torch/lib/libTHC.so.1: undefined symbol: sormqr_
| 1.0 | undefined symbol: sormqr_ - I compiled `pytorch` (using both Python 2 and Python 3) with CUDA support on Ubuntu 16.04 having gcc 4.8.5. The install process terminated with no critical errors.
Torch is already installed on the same machine and works fine.
When importing `pytorch` I get the following error:
----> 1 import torch
/home/tudor/anaconda2/lib/python2.7/site-packages/torch/__init__.pyc in <module>()
43 sys.setdlopenflags(_dl_flags.RTLD_GLOBAL | _dl_flags.RTLD_NOW)
44
---> 45 from torch._C import *
46
47 __all__ += [name for name in dir(_C)
ImportError: /home/tudor/anaconda2/lib/python2.7/site-packages/torch/lib/libTHC.so.1: undefined symbol: sormqr_
| non_main | undefined symbol sormqr i compiled pytorch using both python and python with cuda support on ubuntu having gcc the install process terminated with no critical errors torch is already installed on the same machine and works fine when importing pytorch i get the following error import torch home tudor lib site packages torch init pyc in sys setdlopenflags dl flags rtld global dl flags rtld now from torch c import all name for name in dir c importerror home tudor lib site packages torch lib libthc so undefined symbol sormqr | 0 |
521,415 | 15,109,299,655 | IssuesEvent | 2021-02-08 17:40:03 | infiniteautomation/ma-core-public | https://api.github.com/repos/infiniteautomation/ma-core-public | closed | Script API - Don't allow PermissionService.runAsSystemAdmin | High Priority Item | One way or another we need to prevent this method from being available in the new script context. Either by not injecting this service or moving/shadowing the method. | 1.0 | Script API - Don't allow PermissionService.runAsSystemAdmin - One way or another we need to prevent this method from being available in the new script context. Either by not injecting this service or moving/shadowing the method. | non_main | script api don t allow permissionservice runassystemadmin one way or another we need to prevent this method from being available in the new script context either by not injecting this service or moving shadowing the method | 0 |
391 | 3,436,121,182 | IssuesEvent | 2015-12-12 04:26:00 | caskroom/homebrew-cask | https://api.github.com/repos/caskroom/homebrew-cask | opened | Should we deprecate cask DSL versions? | awaiting maintainer feedback discussion | With #15381 out of the way, casks should no longer be out of sync with the core library. From here on out, no cask should ever be using a DSL that's newer than the one in core (since updating casks requires running `brew update`, which will update core as well).
So what's the point of maintaining a DSL version? Keep in mind that if we do so, every time a cask update includes a new DSL element, we'll need to remember to bump the header as well. | True | Should we deprecate cask DSL versions? - With #15381 out of the way, casks should no longer be out of sync with the core library. From here on out, no cask should ever be using a DSL that's newer than the one in core (since updating casks requires running `brew update`, which will update core as well).
So what's the point of maintaining a DSL version? Keep in mind that if we do so, every time a cask update includes a new DSL element, we'll need to remember to bump the header as well. | main | should we deprecate cask dsl versions with out of the way casks should no longer be out of sync with the core library from here on out no cask should ever be using a dsl that s newer than the one in core since updating casks requires running brew update which will update core as well so what s the point of maintaining a dsl version keep in mind that if we do so every time a cask update includes a new dsl element we ll need to remember to bump the header as well | 1 |
233,421 | 18,984,832,060 | IssuesEvent | 2021-11-21 14:41:36 | codezonediitj/pydatastructs | https://api.github.com/repos/codezonediitj/pydatastructs | opened | Add pydatastructs.test function to run tests | enhancement testing | #### Description of the problem
<!--Please provide a clear and details information of the bug/data structure to be added.-->
The above function would make it easier for the user to verify the installation of PyDataStructs APIs.
#### Example of the problem
<!--Provide a reproducible example code which is causing the bug to appear. Leave this section if the problem is not a bug.-->
#### References/Other comments
| 1.0 | Add pydatastructs.test function to run tests - #### Description of the problem
<!--Please provide a clear and details information of the bug/data structure to be added.-->
The above function would make it easier for the user to verify the installation of PyDataStructs APIs.
#### Example of the problem
<!--Provide a reproducible example code which is causing the bug to appear. Leave this section if the problem is not a bug.-->
#### References/Other comments
| non_main | add pydatastructs test function to run tests description of the problem the above function would make it easier for the user to verify the installation of pydatastructs apis example of the problem references other comments | 0 |
1,844 | 6,577,380,037 | IssuesEvent | 2017-09-12 00:30:24 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | ec2_ami_find is_public option appears to have the opposite effect on searches | affects_2.0 aws bug_report cloud waiting_on_maintainer | ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
ec2_ami_find
##### ANSIBLE VERSION
```
ansible 2.0.2.0
```
##### CONFIGURATION
##### OS / ENVIRONMENT
Running from: OS X 10.11.4
Managing: N/A
##### SUMMARY
ec2_ami_find's `is_public` appears to have the opposite effect on searches.
##### STEPS TO REPRODUCE
Run the following playbook.
```
---
- name: Find base ubuntu image
hosts: localhost
gather_facts: no
tasks:
- name: Find latest Ubuntu AMI
ec2_ami_find:
name: "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-*"
owner: "099720109477"
region: us-west-2
sort: name
sort_order: descending
is_public: no
register: ami
- debug: var=ami
```
##### EXPECTED RESULTS
No AMIs should be found.
##### ACTUAL RESULTS
Several public AMIs are found.
```
No config file found; using defaults
Loaded callback default of type stdout, v2.0
PLAYBOOK: base-image-playbook.yml **********************************************
1 plays in base-image-playbook.yml
PLAY [Find base ubuntu image] **************************************************
TASK [Find latest Ubuntu AMI] **************************************************
task path: /Users/mike/courseload/ansible/aws/base-amis/base-image-playbook.yml:7
ESTABLISH LOCAL CONNECTION FOR USER: mike
localhost EXEC /bin/sh -c '( umask 22 && mkdir -p "` echo $HOME/.ansible/tmp/ansible-tmp-1463072481.44-30922191967772 `" && echo "` echo $HOME/.ansible/tmp/ansible-tmp-1463072481.44-30922191967772 `" )'
localhost PUT /var/folders/_r/5z5t3kln6yn8r3jgrbyvbb6r0000gn/T/tmpADAGwX TO /Users/mike/.ansible/tmp/ansible-tmp-1463072481.44-30922191967772/ec2_ami_find
localhost EXEC /bin/sh -c 'LANG=en_US.UTF-8 LC_ALL=en_US.UTF-8 LC_MESSAGES=en_US.UTF-8 /usr/bin/python /Users/mike/.ansible/tmp/ansible-tmp-1463072481.44-30922191967772/ec2_ami_find; rm -rf "/Users/mike/.ansible/tmp/ansible-tmp-1463072481.44-30922191967772/" > /dev/null 2>&1'
ok: [localhost] => {"changed": false, "invocation": {"module_args": {"ami_id": null, "ami_tags": null, "architecture": null, "aws_access_key": null, "aws_secret_key": null, "ec2_url": null, "hypervisor": null, "is_public": false, "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-*", "no_result_action": "success", "owner": "099720109477", "platform": null, "profile": null, "region": "us-west-2", "security_token": null, "sort": "name", "sort_end": null, "sort_order": "descending", "sort_start": null, "sort_tag": null, "state": "available", "validate_certs": true, "virtualization_type": null}, "module_name": "ec2_ami_find"}, "results": [{"ami_id": "ami-0dc73a6d", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-df2c1224", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2016-05-10T11:55:12.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160509.1", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160509.1", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-3f9f6b5f", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-50548f0b", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2016-04-06T22:01:12.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160406", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160406", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-8ba74eeb", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-b9bbc2e0", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2016-03-15T08:30:19.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160314", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160314", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-412dcf21", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-22204477", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2016-02-23T13:52:53.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160222", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160222", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-6f22c10f", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-275e087e", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2016-02-18T01:36:38.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160217.1", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160217.1", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-a1c721c1", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-d0c42c92", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2016-02-02T12:11:03.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160201", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160201", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-401ffa20", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-4d8efa0f", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2016-01-20T12:14:39.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160119", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160119", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-9cbea4fd", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-5dd4561f", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2016-01-15T22:10:59.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160114.5", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160114.5", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-47465826", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-e5bd36a7", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-12-20T01:45:09.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151218", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151218", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-28879849", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-733e3421", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-12-18T09:40:13.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151217", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151217", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-e54f5f84", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-43091c01", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-11-18T08:16:55.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151117", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151117", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-06a4b367", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-d18d8789", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-11-06T23:02:55.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151105", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151105", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-96e605a5", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-f907c8a5", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-10-20T09:03:36.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151019", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151019", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-281eff1b", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-21fecb62", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-10-15T20:43:20.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151015", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151015", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-20d73013", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-e08d28a6", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-10-09T08:47:39.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151008", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151008", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-e0aa4dd3", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-7d9da826", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-10-08T08:57:15.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151007", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151007", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-16e30725", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-f4006fa4", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-10-06T09:25:57.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151005", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151005", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-09f8e239", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-9a178cc2", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-10-01T11:23:38.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150930", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150930", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-9bbea5ab", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-367f3474", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-09-29T11:13:09.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150928", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150928", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-1de9f12d", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-6414e627", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-09-25T13:37:12.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150924", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150924", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-c53c21f5", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-b75f10e7", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-09-09T05:58:40.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150908", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150908", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-e91605d9", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-96f011c7", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-09-02T05:14:31.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150901.1", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150901.1", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-bbd5c08b", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-5a8dfa19", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-08-15T08:11:01.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150814", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150814", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-b5736685", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-45cf0117", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-08-14T07:14:08.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150813", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150813", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-539d9763", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-4d39c40b", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-08-13T08:49:30.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150812", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150812", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-c5616bf5", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-11898c4d", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-08-11T11:43:15.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150810", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150810", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-bf868e8f", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-7adde43a", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-08-06T19:28:39.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150805", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150805", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-a56d6495", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-53c3440c", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-08-01T09:04:22.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150731", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150731", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-d9f5fae9", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-d5874884", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-07-28T07:13:16.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150727", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150727", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-e5b8b4d5", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-ff17f1bd", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-07-25T05:06:19.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150724", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150724", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-975b5da7", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-e66090bc", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-06-30T09:14:05.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150629", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150629", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-ade1d99d", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-48daf60e", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-06-09T17:18:18.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150609", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150609", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-7b0d354b", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-14f47d54", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-06-09T03:53:54.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150608", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150608", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-0f675e3f", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-df61a59d", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-06-04T08:13:14.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150603", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150603", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-65e8d755", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-e39793be", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-05-29T10:14:50.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150528", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150528", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-d986b7e9", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-84189ad9", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-05-07T08:13:35.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150506", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150506", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-67526757", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-58822d1a", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-04-17T12:05:37.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150417", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150417", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-595b7069", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-f15377ab", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-04-09T08:51:42.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150408.1", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150408.1", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-7f89a64f", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-9108fdce", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-03-25T23:55:53.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150325", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150325", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-cb1536fb", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-c78bb49e", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-03-05T11:02:22.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150305", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150305", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-fd3818cd", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-fc5fcba9", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-02-28T07:14:48.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150227.2", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150227.2", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-0ba6873b", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-30ef3d72", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-02-26T06:02:31.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150225.2", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150225.2", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-990a2fa9", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-03180082", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-02-10T05:22:23.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150209.1", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150209.1", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-3bebb50b", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-2b7385aa", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-01-23T10:56:41.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150123", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150123", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-978dd9a7", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-f7f8df7a", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-11-26T01:49:55.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20141125", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20141125", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-cd5311fd", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-c5762a0c", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-09-30T00:18:42.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140927", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140927", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-efd497df", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-a8044961", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-09-26T16:04:28.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140926", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140926", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-2799da17", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-eb3a4822", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-09-25T14:06:50.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140924", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140924", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-cf397aff", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-7e9cf9b7", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-09-23T14:15:01.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140923", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140923", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-2d9add1d", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-ac55ed5a", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-08-29T18:45:35.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140829", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140829", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-f1ce8bc1", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-edd3e31a", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-08-16T22:56:58.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140816", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140816", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-7f6e2b4f", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-4085d5b7", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-08-14T00:49:54.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140813", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140813", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-9986fea9", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-f1898a05", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-07-25T08:28:27.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140724", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140724", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-f34032c3", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-7d04a288", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-06-08T00:30:16.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140607.1", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140607.1", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-f13e4dc1", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-9cdce36e", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-05-29T19:07:23.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140528", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140528", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-6ac2a85a", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-82da0571", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-04-17T06:17:06.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140416.1", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140416.1", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}]}
TASK [debug] *******************************************************************
task path: /Users/mike/courseload/ansible/aws/base-amis/base-image-playbook.yml:17
ok: [localhost] => {
"ami": {
"changed": false,
"results": [
{
"ami_id": "ami-0dc73a6d",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-df2c1224",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2016-05-10T11:55:12.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160509.1",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160509.1",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-3f9f6b5f",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-50548f0b",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2016-04-06T22:01:12.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160406",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160406",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-8ba74eeb",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-b9bbc2e0",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2016-03-15T08:30:19.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160314",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160314",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-412dcf21",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-22204477",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2016-02-23T13:52:53.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160222",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160222",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-6f22c10f",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-275e087e",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2016-02-18T01:36:38.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160217.1",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160217.1",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-a1c721c1",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-d0c42c92",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2016-02-02T12:11:03.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160201",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160201",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-401ffa20",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-4d8efa0f",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2016-01-20T12:14:39.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160119",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160119",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-9cbea4fd",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-5dd4561f",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2016-01-15T22:10:59.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160114.5",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160114.5",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-47465826",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-e5bd36a7",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-12-20T01:45:09.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151218",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151218",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-28879849",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-733e3421",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-12-18T09:40:13.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151217",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151217",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-e54f5f84",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-43091c01",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-11-18T08:16:55.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151117",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151117",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-06a4b367",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-d18d8789",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-11-06T23:02:55.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151105",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151105",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-96e605a5",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-f907c8a5",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-10-20T09:03:36.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151019",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151019",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-281eff1b",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-21fecb62",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-10-15T20:43:20.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151015",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151015",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-20d73013",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-e08d28a6",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-10-09T08:47:39.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151008",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151008",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-e0aa4dd3",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-7d9da826",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-10-08T08:57:15.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151007",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151007",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-16e30725",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-f4006fa4",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-10-06T09:25:57.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151005",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151005",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-09f8e239",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-9a178cc2",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-10-01T11:23:38.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150930",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150930",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-9bbea5ab",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-367f3474",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-09-29T11:13:09.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150928",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150928",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-1de9f12d",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-6414e627",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-09-25T13:37:12.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150924",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150924",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-c53c21f5",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-b75f10e7",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-09-09T05:58:40.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150908",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150908",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-e91605d9",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-96f011c7",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-09-02T05:14:31.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150901.1",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150901.1",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-bbd5c08b",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-5a8dfa19",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-08-15T08:11:01.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150814",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150814",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-b5736685",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-45cf0117",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-08-14T07:14:08.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150813",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150813",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-539d9763",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-4d39c40b",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-08-13T08:49:30.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150812",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150812",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-c5616bf5",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-11898c4d",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-08-11T11:43:15.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150810",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150810",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-bf868e8f",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-7adde43a",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-08-06T19:28:39.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150805",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150805",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-a56d6495",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-53c3440c",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-08-01T09:04:22.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150731",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150731",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-d9f5fae9",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-d5874884",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-07-28T07:13:16.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150727",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150727",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-e5b8b4d5",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-ff17f1bd",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-07-25T05:06:19.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150724",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150724",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-975b5da7",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-e66090bc",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-06-30T09:14:05.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150629",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150629",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-ade1d99d",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-48daf60e",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-06-09T17:18:18.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150609",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150609",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-7b0d354b",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-14f47d54",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-06-09T03:53:54.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150608",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150608",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-0f675e3f",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-df61a59d",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-06-04T08:13:14.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150603",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150603",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-65e8d755",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-e39793be",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-05-29T10:14:50.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150528",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150528",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-d986b7e9",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-84189ad9",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-05-07T08:13:35.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150506",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150506",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-67526757",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-58822d1a",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-04-17T12:05:37.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150417",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150417",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-595b7069",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-f15377ab",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-04-09T08:51:42.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150408.1",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150408.1",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-7f89a64f",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-9108fdce",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-03-25T23:55:53.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150325",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150325",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-cb1536fb",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-c78bb49e",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-03-05T11:02:22.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150305",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150305",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-fd3818cd",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-fc5fcba9",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-02-28T07:14:48.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150227.2",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150227.2",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-0ba6873b",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-30ef3d72",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-02-26T06:02:31.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150225.2",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150225.2",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-990a2fa9",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-03180082",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-02-10T05:22:23.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150209.1",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150209.1",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-3bebb50b",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-2b7385aa",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-01-23T10:56:41.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150123",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150123",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-978dd9a7",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-f7f8df7a",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-11-26T01:49:55.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20141125",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20141125",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-cd5311fd",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-c5762a0c",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-09-30T00:18:42.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140927",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140927",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-efd497df",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-a8044961",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-09-26T16:04:28.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140926",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140926",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-2799da17",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-eb3a4822",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-09-25T14:06:50.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140924",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140924",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-cf397aff",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-7e9cf9b7",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-09-23T14:15:01.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140923",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140923",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-2d9add1d",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-ac55ed5a",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-08-29T18:45:35.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140829",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140829",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-f1ce8bc1",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-edd3e31a",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-08-16T22:56:58.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140816",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140816",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-7f6e2b4f",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-4085d5b7",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-08-14T00:49:54.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140813",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140813",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-9986fea9",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-f1898a05",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-07-25T08:28:27.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140724",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140724",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-f34032c3",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-7d04a288",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-06-08T00:30:16.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140607.1",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140607.1",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-f13e4dc1",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-9cdce36e",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-05-29T19:07:23.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140528",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140528",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-6ac2a85a",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-82da0571",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-04-17T06:17:06.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140416.1",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140416.1",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
}
]
}
}
PLAY RECAP *********************************************************************
localhost : ok=2 changed=0 unreachable=0 failed=0
```
| True | ec2_ami_find is_public option appears to have the opposite effect on searches - ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
ec2_ami_find
##### ANSIBLE VERSION
```
ansible 2.0.2.0
```
##### CONFIGURATION
##### OS / ENVIRONMENT
Running from: OS X 10.11.4
Managing: N/A
##### SUMMARY
ec2_ami_find's `is_public` appears to have the opposite effect on searches.
##### STEPS TO REPRODUCE
Run the following playbook.
```
---
- name: Find base ubuntu image
hosts: localhost
gather_facts: no
tasks:
- name: Find latest Ubuntu AMI
ec2_ami_find:
name: "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-*"
owner: "099720109477"
region: us-west-2
sort: name
sort_order: descending
is_public: no
register: ami
- debug: var=ami
```
##### EXPECTED RESULTS
No AMIs should be found.
##### ACTUAL RESULTS
Several public AMIs are found.
```
No config file found; using defaults
Loaded callback default of type stdout, v2.0
PLAYBOOK: base-image-playbook.yml **********************************************
1 plays in base-image-playbook.yml
PLAY [Find base ubuntu image] **************************************************
TASK [Find latest Ubuntu AMI] **************************************************
task path: /Users/mike/courseload/ansible/aws/base-amis/base-image-playbook.yml:7
ESTABLISH LOCAL CONNECTION FOR USER: mike
localhost EXEC /bin/sh -c '( umask 22 && mkdir -p "` echo $HOME/.ansible/tmp/ansible-tmp-1463072481.44-30922191967772 `" && echo "` echo $HOME/.ansible/tmp/ansible-tmp-1463072481.44-30922191967772 `" )'
localhost PUT /var/folders/_r/5z5t3kln6yn8r3jgrbyvbb6r0000gn/T/tmpADAGwX TO /Users/mike/.ansible/tmp/ansible-tmp-1463072481.44-30922191967772/ec2_ami_find
localhost EXEC /bin/sh -c 'LANG=en_US.UTF-8 LC_ALL=en_US.UTF-8 LC_MESSAGES=en_US.UTF-8 /usr/bin/python /Users/mike/.ansible/tmp/ansible-tmp-1463072481.44-30922191967772/ec2_ami_find; rm -rf "/Users/mike/.ansible/tmp/ansible-tmp-1463072481.44-30922191967772/" > /dev/null 2>&1'
ok: [localhost] => {"changed": false, "invocation": {"module_args": {"ami_id": null, "ami_tags": null, "architecture": null, "aws_access_key": null, "aws_secret_key": null, "ec2_url": null, "hypervisor": null, "is_public": false, "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-*", "no_result_action": "success", "owner": "099720109477", "platform": null, "profile": null, "region": "us-west-2", "security_token": null, "sort": "name", "sort_end": null, "sort_order": "descending", "sort_start": null, "sort_tag": null, "state": "available", "validate_certs": true, "virtualization_type": null}, "module_name": "ec2_ami_find"}, "results": [{"ami_id": "ami-0dc73a6d", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-df2c1224", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2016-05-10T11:55:12.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160509.1", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160509.1", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-3f9f6b5f", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-50548f0b", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2016-04-06T22:01:12.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160406", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160406", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-8ba74eeb", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-b9bbc2e0", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2016-03-15T08:30:19.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160314", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160314", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-412dcf21", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-22204477", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2016-02-23T13:52:53.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160222", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160222", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-6f22c10f", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-275e087e", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2016-02-18T01:36:38.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160217.1", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160217.1", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-a1c721c1", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-d0c42c92", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2016-02-02T12:11:03.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160201", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160201", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-401ffa20", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-4d8efa0f", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2016-01-20T12:14:39.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160119", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160119", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-9cbea4fd", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-5dd4561f", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2016-01-15T22:10:59.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160114.5", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160114.5", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-47465826", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-e5bd36a7", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-12-20T01:45:09.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151218", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151218", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-28879849", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-733e3421", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-12-18T09:40:13.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151217", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151217", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-e54f5f84", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-43091c01", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-11-18T08:16:55.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151117", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151117", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-06a4b367", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-d18d8789", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-11-06T23:02:55.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151105", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151105", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-96e605a5", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-f907c8a5", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-10-20T09:03:36.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151019", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151019", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-281eff1b", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-21fecb62", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-10-15T20:43:20.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151015", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151015", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-20d73013", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-e08d28a6", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-10-09T08:47:39.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151008", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151008", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-e0aa4dd3", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-7d9da826", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-10-08T08:57:15.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151007", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151007", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-16e30725", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-f4006fa4", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-10-06T09:25:57.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151005", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151005", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-09f8e239", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-9a178cc2", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-10-01T11:23:38.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150930", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150930", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-9bbea5ab", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-367f3474", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-09-29T11:13:09.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150928", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150928", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-1de9f12d", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-6414e627", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-09-25T13:37:12.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150924", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150924", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-c53c21f5", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-b75f10e7", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-09-09T05:58:40.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150908", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150908", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-e91605d9", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-96f011c7", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-09-02T05:14:31.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150901.1", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150901.1", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-bbd5c08b", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-5a8dfa19", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-08-15T08:11:01.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150814", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150814", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-b5736685", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-45cf0117", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-08-14T07:14:08.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150813", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150813", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-539d9763", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-4d39c40b", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-08-13T08:49:30.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150812", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150812", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-c5616bf5", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-11898c4d", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-08-11T11:43:15.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150810", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150810", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-bf868e8f", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-7adde43a", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-08-06T19:28:39.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150805", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150805", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-a56d6495", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-53c3440c", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-08-01T09:04:22.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150731", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150731", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-d9f5fae9", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-d5874884", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-07-28T07:13:16.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150727", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150727", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-e5b8b4d5", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-ff17f1bd", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-07-25T05:06:19.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150724", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150724", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-975b5da7", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-e66090bc", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-06-30T09:14:05.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150629", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150629", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-ade1d99d", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-48daf60e", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-06-09T17:18:18.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150609", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150609", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-7b0d354b", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-14f47d54", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-06-09T03:53:54.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150608", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150608", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-0f675e3f", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-df61a59d", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-06-04T08:13:14.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150603", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150603", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-65e8d755", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-e39793be", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-05-29T10:14:50.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150528", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150528", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-d986b7e9", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-84189ad9", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-05-07T08:13:35.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150506", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150506", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-67526757", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-58822d1a", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-04-17T12:05:37.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150417", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150417", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-595b7069", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-f15377ab", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-04-09T08:51:42.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150408.1", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150408.1", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-7f89a64f", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-9108fdce", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-03-25T23:55:53.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150325", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150325", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-cb1536fb", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-c78bb49e", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-03-05T11:02:22.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150305", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150305", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-fd3818cd", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-fc5fcba9", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-02-28T07:14:48.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150227.2", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150227.2", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-0ba6873b", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-30ef3d72", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-02-26T06:02:31.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150225.2", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150225.2", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-990a2fa9", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-03180082", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-02-10T05:22:23.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150209.1", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150209.1", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-3bebb50b", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-2b7385aa", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2015-01-23T10:56:41.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150123", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150123", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-978dd9a7", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-f7f8df7a", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-11-26T01:49:55.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20141125", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20141125", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-cd5311fd", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-c5762a0c", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-09-30T00:18:42.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140927", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140927", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-efd497df", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-a8044961", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-09-26T16:04:28.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140926", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140926", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-2799da17", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-eb3a4822", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-09-25T14:06:50.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140924", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140924", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-cf397aff", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-7e9cf9b7", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-09-23T14:15:01.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140923", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140923", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-2d9add1d", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-ac55ed5a", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-08-29T18:45:35.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140829", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140829", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-f1ce8bc1", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-edd3e31a", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-08-16T22:56:58.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140816", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140816", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-7f6e2b4f", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-4085d5b7", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-08-14T00:49:54.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140813", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140813", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-9986fea9", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-f1898a05", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-07-25T08:28:27.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140724", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140724", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-f34032c3", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-7d04a288", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-06-08T00:30:16.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140607.1", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140607.1", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-f13e4dc1", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-9cdce36e", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-05-29T19:07:23.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140528", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140528", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}, {"ami_id": "ami-6ac2a85a", "architecture": "x86_64", "block_device_mapping": {"/dev/sda1": {"delete_on_termination": true, "encrypted": false, "size": 8, "snapshot_id": "snap-82da0571", "volume_type": "standard"}, "/dev/sdb": {"delete_on_termination": false, "encrypted": null, "size": null, "snapshot_id": null, "volume_type": null}}, "creationDate": "2014-04-17T06:17:06.000Z", "description": null, "hypervisor": "xen", "is_public": true, "kernel_id": "aki-fc8f11cc", "location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140416.1", "name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140416.1", "owner_id": "099720109477", "platform": null, "root_device_name": "/dev/sda1", "root_device_type": "ebs", "state": "available", "tags": {}, "virtualization_type": "paravirtual"}]}
TASK [debug] *******************************************************************
task path: /Users/mike/courseload/ansible/aws/base-amis/base-image-playbook.yml:17
ok: [localhost] => {
"ami": {
"changed": false,
"results": [
{
"ami_id": "ami-0dc73a6d",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-df2c1224",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2016-05-10T11:55:12.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160509.1",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160509.1",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-3f9f6b5f",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-50548f0b",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2016-04-06T22:01:12.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160406",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160406",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-8ba74eeb",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-b9bbc2e0",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2016-03-15T08:30:19.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160314",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160314",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-412dcf21",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-22204477",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2016-02-23T13:52:53.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160222",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160222",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-6f22c10f",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-275e087e",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2016-02-18T01:36:38.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160217.1",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160217.1",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-a1c721c1",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-d0c42c92",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2016-02-02T12:11:03.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160201",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160201",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-401ffa20",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-4d8efa0f",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2016-01-20T12:14:39.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160119",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160119",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-9cbea4fd",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-5dd4561f",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2016-01-15T22:10:59.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160114.5",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20160114.5",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-47465826",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-e5bd36a7",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-12-20T01:45:09.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151218",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151218",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-28879849",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-733e3421",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-12-18T09:40:13.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151217",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151217",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-e54f5f84",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-43091c01",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-11-18T08:16:55.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151117",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151117",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-06a4b367",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-d18d8789",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-11-06T23:02:55.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151105",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151105",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-96e605a5",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-f907c8a5",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-10-20T09:03:36.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151019",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151019",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-281eff1b",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-21fecb62",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-10-15T20:43:20.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151015",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151015",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-20d73013",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-e08d28a6",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-10-09T08:47:39.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151008",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151008",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-e0aa4dd3",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-7d9da826",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-10-08T08:57:15.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151007",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151007",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-16e30725",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-f4006fa4",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-10-06T09:25:57.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151005",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20151005",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-09f8e239",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-9a178cc2",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-10-01T11:23:38.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150930",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150930",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-9bbea5ab",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-367f3474",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-09-29T11:13:09.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150928",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150928",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-1de9f12d",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-6414e627",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-09-25T13:37:12.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150924",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150924",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-c53c21f5",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-b75f10e7",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-09-09T05:58:40.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150908",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150908",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-e91605d9",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-96f011c7",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-09-02T05:14:31.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150901.1",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150901.1",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-bbd5c08b",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-5a8dfa19",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-08-15T08:11:01.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150814",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150814",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-b5736685",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-45cf0117",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-08-14T07:14:08.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150813",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150813",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-539d9763",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-4d39c40b",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-08-13T08:49:30.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150812",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150812",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-c5616bf5",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-11898c4d",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-08-11T11:43:15.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150810",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150810",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-bf868e8f",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-7adde43a",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-08-06T19:28:39.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150805",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150805",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-a56d6495",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-53c3440c",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-08-01T09:04:22.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150731",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150731",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-d9f5fae9",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-d5874884",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-07-28T07:13:16.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150727",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150727",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-e5b8b4d5",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-ff17f1bd",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-07-25T05:06:19.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150724",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150724",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-975b5da7",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-e66090bc",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-06-30T09:14:05.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150629",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150629",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-ade1d99d",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-48daf60e",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-06-09T17:18:18.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150609",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150609",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-7b0d354b",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-14f47d54",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-06-09T03:53:54.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150608",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150608",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-0f675e3f",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-df61a59d",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-06-04T08:13:14.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150603",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150603",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-65e8d755",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-e39793be",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-05-29T10:14:50.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150528",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150528",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-d986b7e9",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-84189ad9",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-05-07T08:13:35.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150506",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150506",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-67526757",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-58822d1a",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-04-17T12:05:37.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150417",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150417",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-595b7069",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-f15377ab",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-04-09T08:51:42.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150408.1",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150408.1",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-7f89a64f",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-9108fdce",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-03-25T23:55:53.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150325",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150325",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-cb1536fb",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-c78bb49e",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-03-05T11:02:22.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150305",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150305",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-fd3818cd",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-fc5fcba9",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-02-28T07:14:48.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150227.2",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150227.2",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-0ba6873b",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-30ef3d72",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-02-26T06:02:31.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150225.2",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150225.2",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-990a2fa9",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-03180082",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-02-10T05:22:23.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150209.1",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150209.1",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-3bebb50b",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-2b7385aa",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2015-01-23T10:56:41.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150123",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20150123",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-978dd9a7",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-f7f8df7a",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-11-26T01:49:55.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20141125",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20141125",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-cd5311fd",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-c5762a0c",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-09-30T00:18:42.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140927",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140927",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-efd497df",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-a8044961",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-09-26T16:04:28.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140926",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140926",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-2799da17",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-eb3a4822",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-09-25T14:06:50.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140924",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140924",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-cf397aff",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-7e9cf9b7",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-09-23T14:15:01.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140923",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140923",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-2d9add1d",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-ac55ed5a",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-08-29T18:45:35.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140829",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140829",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-f1ce8bc1",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-edd3e31a",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-08-16T22:56:58.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140816",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140816",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-7f6e2b4f",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-4085d5b7",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-08-14T00:49:54.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140813",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140813",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-9986fea9",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-f1898a05",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-07-25T08:28:27.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140724",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140724",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-f34032c3",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-7d04a288",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-06-08T00:30:16.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140607.1",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140607.1",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-f13e4dc1",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-9cdce36e",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-05-29T19:07:23.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140528",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140528",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
},
{
"ami_id": "ami-6ac2a85a",
"architecture": "x86_64",
"block_device_mapping": {
"/dev/sda1": {
"delete_on_termination": true,
"encrypted": false,
"size": 8,
"snapshot_id": "snap-82da0571",
"volume_type": "standard"
},
"/dev/sdb": {
"delete_on_termination": false,
"encrypted": null,
"size": null,
"snapshot_id": null,
"volume_type": null
}
},
"creationDate": "2014-04-17T06:17:06.000Z",
"description": null,
"hypervisor": "xen",
"is_public": true,
"kernel_id": "aki-fc8f11cc",
"location": "099720109477/ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140416.1",
"name": "ubuntu/images/ebs/ubuntu-trusty-14.04-amd64-server-20140416.1",
"owner_id": "099720109477",
"platform": null,
"root_device_name": "/dev/sda1",
"root_device_type": "ebs",
"state": "available",
"tags": {},
"virtualization_type": "paravirtual"
}
]
}
}
PLAY RECAP *********************************************************************
localhost : ok=2 changed=0 unreachable=0 failed=0
```
| main | ami find is public option appears to have the opposite effect on searches issue type bug report component name ami find ansible version ansible configuration os environment running from os x managing n a summary ami find s is public appears to have the opposite effect on searches steps to reproduce run the following playbook name find base ubuntu image hosts localhost gather facts no tasks name find latest ubuntu ami ami find name ubuntu images ebs ubuntu trusty server owner region us west sort name sort order descending is public no register ami debug var ami expected results no amis should be found actual results several public amis are found no config file found using defaults loaded callback default of type stdout playbook base image playbook yml plays in base image playbook yml play task task path users mike courseload ansible aws base amis base image playbook yml establish local connection for user mike localhost exec bin sh c umask mkdir p echo home ansible tmp ansible tmp echo echo home ansible tmp ansible tmp localhost put var folders r t tmpadagwx to users mike ansible tmp ansible tmp ami find localhost exec bin sh c lang en us utf lc all en us utf lc messages en us utf usr bin python users mike ansible tmp ansible tmp ami find rm rf users mike ansible tmp ansible tmp dev null ok changed false invocation module args ami id null ami tags null architecture null aws access key null aws secret key null url null hypervisor null is public false name ubuntu images ebs ubuntu trusty server no result action success owner platform null profile null region us west security token null sort name sort end null sort order descending sort start null sort tag null state available validate certs true virtualization type null module name ami find results task task path users mike courseload ansible aws base amis base image playbook yml ok ami changed false results ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual ami id ami architecture block device mapping dev delete on termination true encrypted false size snapshot id snap volume type standard dev sdb delete on termination false encrypted null size null snapshot id null volume type null creationdate description null hypervisor xen is public true kernel id aki location ubuntu images ebs ubuntu trusty server name ubuntu images ebs ubuntu trusty server owner id platform null root device name dev root device type ebs state available tags virtualization type paravirtual play recap localhost ok changed unreachable failed | 1 |
4,962 | 25,479,207,790 | IssuesEvent | 2022-11-25 17:57:00 | bazelbuild/intellij | https://api.github.com/repos/bazelbuild/intellij | closed | Run gazelle on project sync | type: feature request P1 lang: go product: IntelliJ topic: sync product: GoLand awaiting-maintainer | ## Problem
For projects that use gazelle, moving a single file is a two-step process: First they must run gazelle, then they must sync to trigger re-indexing if IntelliJ didn't pick those changes up.
Ideally, this would be a single-click action, whereby a user only has to click "sync" after a refactoring is done.
## Proposed Solution
Run Gazelle on sync, at least for full, non-incremental syncs of projects, before we run the bazel build that enables the actual sync.
Regarding performance, Gazelle accepts packages as arguments, so I believe it should be possible to inspect the `.bazelproject` file to gather which packages it should sync, therefore correlating performance to the size of the indexed project.
The changes I imagine would be needed:
- Additional entries in the Bazel Plugin preferences, where the user can specify:
- The label of the Gazelle target to run.
- The frequency of the gazelle runs (on every sync, or only on full syncs).
- Custom logic to derive go packages from the `directories` entry in the `.bazelproject`.
- A call to gazelle during project sync, which would run before even the initial query.
I'm happy to spend the effort of implementing this, but as per the contributing guidelines I thought I'd ask first if this would be an interesting contribution, and if I missed important pieces. | True | Run gazelle on project sync - ## Problem
For projects that use gazelle, moving a single file is a two-step process: First they must run gazelle, then they must sync to trigger re-indexing if IntelliJ didn't pick those changes up.
Ideally, this would be a single-click action, whereby a user only has to click "sync" after a refactoring is done.
## Proposed Solution
Run Gazelle on sync, at least for full, non-incremental syncs of projects, before we run the bazel build that enables the actual sync.
Regarding performance, Gazelle accepts packages as arguments, so I believe it should be possible to inspect the `.bazelproject` file to gather which packages it should sync, therefore correlating performance to the size of the indexed project.
The changes I imagine would be needed:
- Additional entries in the Bazel Plugin preferences, where the user can specify:
- The label of the Gazelle target to run.
- The frequency of the gazelle runs (on every sync, or only on full syncs).
- Custom logic to derive go packages from the `directories` entry in the `.bazelproject`.
- A call to gazelle during project sync, which would run before even the initial query.
I'm happy to spend the effort of implementing this, but as per the contributing guidelines I thought I'd ask first if this would be an interesting contribution, and if I missed important pieces. | main | run gazelle on project sync problem for projects that use gazelle moving a single file is a two step process first they must run gazelle then they must sync to trigger re indexing if intellij didn t pick those changes up ideally this would be a single click action whereby a user only has to click sync after a refactoring is done proposed solution run gazelle on sync at least for full non incremental syncs of projects before we run the bazel build that enables the actual sync regarding performance gazelle accepts packages as arguments so i believe it should be possible to inspect the bazelproject file to gather which packages it should sync therefore correlating performance to the size of the indexed project the changes i imagine would be needed additional entries in the bazel plugin preferences where the user can specify the label of the gazelle target to run the frequency of the gazelle runs on every sync or only on full syncs custom logic to derive go packages from the directories entry in the bazelproject a call to gazelle during project sync which would run before even the initial query i m happy to spend the effort of implementing this but as per the contributing guidelines i thought i d ask first if this would be an interesting contribution and if i missed important pieces | 1 |
385,274 | 26,628,698,270 | IssuesEvent | 2023-01-24 16:14:54 | aptos-labs/aptos-core | https://api.github.com/repos/aptos-labs/aptos-core | closed | [Bug] Document funding by network, explain tutorials are for devnet only | bug documentation P2 | # 🐛 Bug
While testing and editing:
https://aptos.dev/tutorials/your-first-dapp/
I found the CLI didn't immediately recognize the private key of the account I just created.
## To reproduce
1. Open the Wallet and click Create a new wallet. Then click Create account to create an Aptos Account.
2. Copy the private key. You will need it to set up the Aptos CLI in the next section.
3. Run `aptos init` and select the default Devnet network.
4. When it asks for your private key, paste the private key from the Aptos Wallet that you copied earlier.
## Stack trace/error message
Receive the output:
```
No network given, using devnet...
Enter your private key as a hex literal (0x...) [Current: None | No input: Generate new key (or keep one if present)]
0x1bcd66761530b81745a3bf69986b25af4142b8fcd382ae3e74a2ea480ec16a9f
Account 37f1a905dc531a0734d620858fce4bce8ed0681c242250955bd9e7d89987be76 doesn't exist, creating it and funding it with 100000000 Octas
Account 37f1a905dc531a0734d620858fce4bce8ed0681c242250955bd9e7d89987be76 funded successfully
```
See the attached screenshot showing the output and the private key used.
<img width="1298" alt="Screen Shot 2022-10-20 at 10 07 40 AM" src="https://user-images.githubusercontent.com/114445310/197015256-012c2869-a9ce-4429-b9b1-b0e922c0b6b7.png">
I do note two potential issues. The docs contain this tip, rather than a step:
"Ensure that your account has sufficient funds to perform transactions by clicking the Faucet button."
So I haven't been doing that.
Further, the doc suggests to install the Aptos CLI after creating the account, which will surely introduce a delay. But since I have it installed already, I am running `aptos init` directly after creating the account. Perhaps related? | 1.0 | [Bug] Document funding by network, explain tutorials are for devnet only - # 🐛 Bug
While testing and editing:
https://aptos.dev/tutorials/your-first-dapp/
I found the CLI didn't immediately recognize the private key of the account I just created.
## To reproduce
1. Open the Wallet and click Create a new wallet. Then click Create account to create an Aptos Account.
2. Copy the private key. You will need it to set up the Aptos CLI in the next section.
3. Run `aptos init` and select the default Devnet network.
4. When it asks for your private key, paste the private key from the Aptos Wallet that you copied earlier.
## Stack trace/error message
Receive the output:
```
No network given, using devnet...
Enter your private key as a hex literal (0x...) [Current: None | No input: Generate new key (or keep one if present)]
0x1bcd66761530b81745a3bf69986b25af4142b8fcd382ae3e74a2ea480ec16a9f
Account 37f1a905dc531a0734d620858fce4bce8ed0681c242250955bd9e7d89987be76 doesn't exist, creating it and funding it with 100000000 Octas
Account 37f1a905dc531a0734d620858fce4bce8ed0681c242250955bd9e7d89987be76 funded successfully
```
See the attached screenshot showing the output and the private key used.
<img width="1298" alt="Screen Shot 2022-10-20 at 10 07 40 AM" src="https://user-images.githubusercontent.com/114445310/197015256-012c2869-a9ce-4429-b9b1-b0e922c0b6b7.png">
I do note two potential issues. The docs contain this tip, rather than a step:
"Ensure that your account has sufficient funds to perform transactions by clicking the Faucet button."
So I haven't been doing that.
Further, the doc suggests to install the Aptos CLI after creating the account, which will surely introduce a delay. But since I have it installed already, I am running `aptos init` directly after creating the account. Perhaps related? | non_main | document funding by network explain tutorials are for devnet only 🐛 bug while testing and editing i found the cli didn t immediately recognize the private key of the account i just created to reproduce open the wallet and click create a new wallet then click create account to create an aptos account copy the private key you will need it to set up the aptos cli in the next section run aptos init and select the default devnet network when it asks for your private key paste the private key from the aptos wallet that you copied earlier stack trace error message receive the output no network given using devnet enter your private key as a hex literal account doesn t exist creating it and funding it with octas account funded successfully see the attached screenshot showing the output and the private key used img width alt screen shot at am src i do note two potential issues the docs contain this tip rather than a step ensure that your account has sufficient funds to perform transactions by clicking the faucet button so i haven t been doing that further the doc suggests to install the aptos cli after creating the account which will surely introduce a delay but since i have it installed already i am running aptos init directly after creating the account perhaps related | 0 |
278,576 | 30,702,358,289 | IssuesEvent | 2023-07-27 01:23:20 | nidhi7598/linux-3.0.35 | https://api.github.com/repos/nidhi7598/linux-3.0.35 | closed | CVE-2023-1998 (Medium) detected in linux-stable-rtv3.8.6 - autoclosed | Mend: dependency security vulnerability | ## CVE-2023-1998 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv3.8.6</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-3.0.35/commit/4cc6d4a22f88b8effe1090492c1a242ce587b492">4cc6d4a22f88b8effe1090492c1a242ce587b492</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The Linux kernel allows userspace processes to enable mitigations by calling prctl with PR_SET_SPECULATION_CTRL which disables the speculation feature as well as by using seccomp. We had noticed that on VMs of at least one major cloud provider, the kernel still left the victim process exposed to attacks in some cases even after enabling the spectre-BTI mitigation with prctl. The same behavior can be observed on a bare-metal machine when forcing the mitigation to IBRS on boot command line.
This happened because when plain IBRS was enabled (not enhanced IBRS), the kernel had some logic that determined that STIBP was not needed. The IBRS bit implicitly protects against cross-thread branch target injection. However, with legacy IBRS, the IBRS bit was cleared on returning to userspace, due to performance reasons, which disabled the implicit STIBP and left userspace threads vulnerable to cross-thread branch target injection against which STIBP protects.
<p>Publish Date: 2023-04-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-1998>CVE-2023-1998</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2023-1998">https://www.linuxkernelcves.com/cves/CVE-2023-1998</a></p>
<p>Release Date: 2023-04-12</p>
<p>Fix Resolution: v6.1.16,v6.2.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2023-1998 (Medium) detected in linux-stable-rtv3.8.6 - autoclosed - ## CVE-2023-1998 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv3.8.6</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-3.0.35/commit/4cc6d4a22f88b8effe1090492c1a242ce587b492">4cc6d4a22f88b8effe1090492c1a242ce587b492</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The Linux kernel allows userspace processes to enable mitigations by calling prctl with PR_SET_SPECULATION_CTRL which disables the speculation feature as well as by using seccomp. We had noticed that on VMs of at least one major cloud provider, the kernel still left the victim process exposed to attacks in some cases even after enabling the spectre-BTI mitigation with prctl. The same behavior can be observed on a bare-metal machine when forcing the mitigation to IBRS on boot command line.
This happened because when plain IBRS was enabled (not enhanced IBRS), the kernel had some logic that determined that STIBP was not needed. The IBRS bit implicitly protects against cross-thread branch target injection. However, with legacy IBRS, the IBRS bit was cleared on returning to userspace, due to performance reasons, which disabled the implicit STIBP and left userspace threads vulnerable to cross-thread branch target injection against which STIBP protects.
<p>Publish Date: 2023-04-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-1998>CVE-2023-1998</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2023-1998">https://www.linuxkernelcves.com/cves/CVE-2023-1998</a></p>
<p>Release Date: 2023-04-12</p>
<p>Fix Resolution: v6.1.16,v6.2.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_main | cve medium detected in linux stable autoclosed cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files vulnerability details the linux kernel allows userspace processes to enable mitigations by calling prctl with pr set speculation ctrl which disables the speculation feature as well as by using seccomp we had noticed that on vms of at least one major cloud provider the kernel still left the victim process exposed to attacks in some cases even after enabling the spectre bti mitigation with prctl the same behavior can be observed on a bare metal machine when forcing the mitigation to ibrs on boot command line this happened because when plain ibrs was enabled not enhanced ibrs the kernel had some logic that determined that stibp was not needed the ibrs bit implicitly protects against cross thread branch target injection however with legacy ibrs the ibrs bit was cleared on returning to userspace due to performance reasons which disabled the implicit stibp and left userspace threads vulnerable to cross thread branch target injection against which stibp protects publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope changed impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
802,850 | 29,047,503,268 | IssuesEvent | 2023-05-13 19:05:00 | monarch-initiative/mondo | https://api.github.com/repos/monarch-initiative/mondo | closed | [NTR] POLD1-related Polyposis and Colorectal Cancer Syndrome | New term request high priority ClinGen | **Preferred term label:**
POLD1-related polyposis and colorectal cancer syndrome
**Synonyms**
**Definition (free text, please give PubMed ID, if applicable, in format PMID:#######)**
An autosomal dominant hereditary syndrome caused by germline pathogenic POLD1 variants. It is characterized by the presence of colorectal polyps and colorectal cancer.
**Parent term (use [OLS](https://www.ebi.ac.uk/ols/ontologies/mondo), or your favorite ontology browser)**
Polyposis (MONDO:0000147)
Colorectal Cancer (MONDO:0005575)
hereditary neoplastic syndrome (MONDO:0015356)
**Children terms (if applicable)** Should any existing terms that should be moved underneath this new proposed term?
**Your nano-attribution (ORCID)**
If you don't have an ORCID, you can sign up for one [here](https://orcid.org/)
ClinGen Hereditary Cancer GCEP (https://clinicalgenome.org/affiliation/40023/) | 1.0 | [NTR] POLD1-related Polyposis and Colorectal Cancer Syndrome - **Preferred term label:**
POLD1-related polyposis and colorectal cancer syndrome
**Synonyms**
**Definition (free text, please give PubMed ID, if applicable, in format PMID:#######)**
An autosomal dominant hereditary syndrome caused by germline pathogenic POLD1 variants. It is characterized by the presence of colorectal polyps and colorectal cancer.
**Parent term (use [OLS](https://www.ebi.ac.uk/ols/ontologies/mondo), or your favorite ontology browser)**
Polyposis (MONDO:0000147)
Colorectal Cancer (MONDO:0005575)
hereditary neoplastic syndrome (MONDO:0015356)
**Children terms (if applicable)** Should any existing terms that should be moved underneath this new proposed term?
**Your nano-attribution (ORCID)**
If you don't have an ORCID, you can sign up for one [here](https://orcid.org/)
ClinGen Hereditary Cancer GCEP (https://clinicalgenome.org/affiliation/40023/) | non_main | related polyposis and colorectal cancer syndrome preferred term label related polyposis and colorectal cancer syndrome synonyms definition free text please give pubmed id if applicable in format pmid an autosomal dominant hereditary syndrome caused by germline pathogenic variants it is characterized by the presence of colorectal polyps and colorectal cancer parent term use or your favorite ontology browser polyposis mondo colorectal cancer mondo hereditary neoplastic syndrome mondo children terms if applicable should any existing terms that should be moved underneath this new proposed term your nano attribution orcid if you don t have an orcid you can sign up for one clingen hereditary cancer gcep | 0 |
5,123 | 26,121,305,976 | IssuesEvent | 2022-12-28 12:58:55 | Vivelin/SMZ3Randomizer | https://api.github.com/repos/Vivelin/SMZ3Randomizer | closed | Upgrade to .NET 6, enable nullable references, support YAML for configs | :wrench: maintainability | Some basic maintainability stuff.
- [x] Upgrade projects from .NET 5 to .NET 6
- [x] Enable nullable references in all projects
- This might be a big one. We'll have to see.
- [x] Enable YAML configuration support, falling back to JSON if `tracker.yml`, `locations.yml` etc. don't exist.
- YAML should be a more natural and readable format for non-tech people, and is considered a superset of JSON so everything should still be supported.
Depends on:
- #16
- We can't really ask everyone to manually install the .NET runtime again. If it can't be done easily with InnoSetup, we should consider switching, instead. | True | Upgrade to .NET 6, enable nullable references, support YAML for configs - Some basic maintainability stuff.
- [x] Upgrade projects from .NET 5 to .NET 6
- [x] Enable nullable references in all projects
- This might be a big one. We'll have to see.
- [x] Enable YAML configuration support, falling back to JSON if `tracker.yml`, `locations.yml` etc. don't exist.
- YAML should be a more natural and readable format for non-tech people, and is considered a superset of JSON so everything should still be supported.
Depends on:
- #16
- We can't really ask everyone to manually install the .NET runtime again. If it can't be done easily with InnoSetup, we should consider switching, instead. | main | upgrade to net enable nullable references support yaml for configs some basic maintainability stuff upgrade projects from net to net enable nullable references in all projects this might be a big one we ll have to see enable yaml configuration support falling back to json if tracker yml locations yml etc don t exist yaml should be a more natural and readable format for non tech people and is considered a superset of json so everything should still be supported depends on we can t really ask everyone to manually install the net runtime again if it can t be done easily with innosetup we should consider switching instead | 1 |
1,605 | 6,572,392,334 | IssuesEvent | 2017-09-11 01:58:09 | ansible/ansible-modules-extras | https://api.github.com/repos/ansible/ansible-modules-extras | closed | virtual server rule ... already exists in partition | affects_2.2 bug_report networking waiting_on_maintainer | ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
network/f5/bigip_virtual_server.py
##### ANSIBLE VERSION
```
2.2.0
```
##### OS / ENVIRONMENT
N/A
##### SUMMARY
When a virtual server exists and nothing should be done the module is trying to update the virtual server and gives error message "virtual server rule (rulename) already exists in partition"
##### STEPS TO REPRODUCE
Create a virtual server using module. Run the playbook/task again without changing any vars.
##### EXPECTED RESULTS
Nothing
##### ACTUAL RESULTS
Module is trying to modify rules
```
01020066:3: The requested virtual server rule (/parititon/vsname
/partition/irule_name) already exists in partition partition.'"
```
The problem is in this line:
`current_rules = map(lambda x: (x['priority'], x['rule_name']), get_rules(api, name))`
`current_rules = list(map(lambda x: (x['priority'], x['rule_name']), get_rules(api, name)))`
This is added in pull request: https://github.com/ansible/ansible-modules-extras/pull/3129
Regards
Per Bly
| True | virtual server rule ... already exists in partition - ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
network/f5/bigip_virtual_server.py
##### ANSIBLE VERSION
```
2.2.0
```
##### OS / ENVIRONMENT
N/A
##### SUMMARY
When a virtual server exists and nothing should be done the module is trying to update the virtual server and gives error message "virtual server rule (rulename) already exists in partition"
##### STEPS TO REPRODUCE
Create a virtual server using module. Run the playbook/task again without changing any vars.
##### EXPECTED RESULTS
Nothing
##### ACTUAL RESULTS
Module is trying to modify rules
```
01020066:3: The requested virtual server rule (/parititon/vsname
/partition/irule_name) already exists in partition partition.'"
```
The problem is in this line:
`current_rules = map(lambda x: (x['priority'], x['rule_name']), get_rules(api, name))`
`current_rules = list(map(lambda x: (x['priority'], x['rule_name']), get_rules(api, name)))`
This is added in pull request: https://github.com/ansible/ansible-modules-extras/pull/3129
Regards
Per Bly
| main | virtual server rule already exists in partition issue type bug report component name network bigip virtual server py ansible version os environment n a summary when a virtual server exists and nothing should be done the module is trying to update the virtual server and gives error message virtual server rule rulename already exists in partition steps to reproduce create a virtual server using module run the playbook task again without changing any vars expected results nothing actual results module is trying to modify rules the requested virtual server rule parititon vsname partition irule name already exists in partition partition the problem is in this line current rules map lambda x x x get rules api name current rules list map lambda x x x get rules api name this is added in pull request regards per bly | 1 |
3,069 | 11,573,665,117 | IssuesEvent | 2020-02-21 04:30:45 | alacritty/alacritty | https://api.github.com/repos/alacritty/alacritty | closed | Arrow keys frozen until first command executed | A - deps B - bug C - waiting on maintainer DS - X11 F - duplicate S - winit/glutin | When I launch alacritty through i3 (`bindsym $mod+Return exec --no-startup-id alacritty`), the arrow keys freeze and I cannot use them. I can write without problems, but I cannot use "back" to go back, or "up" to access the previous command.
Even If I launch `vim`, the arrows are blocked but the `hjkl` keys work.
But, If I run a command, or even `Ctrl+C`, the arrow keys unfreeze and I can use them.
I tried running `alacritty -vv` from a terminal to see the debug output, but then this freezing doesn't happen (I've tried just `alacritty` and no freezing).
### System
OS: Void Linux (5.4.8_1 kernel), zsh 5.7.1
Version: 0.4.1
Linux/BSD: i3wm-gaps (4.17.1), compton
Windows: PTY
### Logs
Crashes: None
Font/Terminal size: `New num_cols is 192 and num_lines is 47`, `Width: 1920, Height: 1048`
Keyboard and bindings:
```
key_bindings:
- { key: V, mods: Control|Shift, action: Paste }
- { key: C, mods: Control|Shift, action: Copy }
- { key: Equals, mods: Control, action: ResetFontSize }
- { key: Add, mods: Control, action: IncreaseFontSize }
- { key: Subtract, mods: Control, action: DecreaseFontSize }
- { key: Minus, mods: Control, action: DecreaseFontSize }
```
EDIT: Apparently, changing focus using the $mod seems to fix the issue (#2906), but it happens every time I open the terminal | True | Arrow keys frozen until first command executed - When I launch alacritty through i3 (`bindsym $mod+Return exec --no-startup-id alacritty`), the arrow keys freeze and I cannot use them. I can write without problems, but I cannot use "back" to go back, or "up" to access the previous command.
Even If I launch `vim`, the arrows are blocked but the `hjkl` keys work.
But, If I run a command, or even `Ctrl+C`, the arrow keys unfreeze and I can use them.
I tried running `alacritty -vv` from a terminal to see the debug output, but then this freezing doesn't happen (I've tried just `alacritty` and no freezing).
### System
OS: Void Linux (5.4.8_1 kernel), zsh 5.7.1
Version: 0.4.1
Linux/BSD: i3wm-gaps (4.17.1), compton
Windows: PTY
### Logs
Crashes: None
Font/Terminal size: `New num_cols is 192 and num_lines is 47`, `Width: 1920, Height: 1048`
Keyboard and bindings:
```
key_bindings:
- { key: V, mods: Control|Shift, action: Paste }
- { key: C, mods: Control|Shift, action: Copy }
- { key: Equals, mods: Control, action: ResetFontSize }
- { key: Add, mods: Control, action: IncreaseFontSize }
- { key: Subtract, mods: Control, action: DecreaseFontSize }
- { key: Minus, mods: Control, action: DecreaseFontSize }
```
EDIT: Apparently, changing focus using the $mod seems to fix the issue (#2906), but it happens every time I open the terminal | main | arrow keys frozen until first command executed when i launch alacritty through bindsym mod return exec no startup id alacritty the arrow keys freeze and i cannot use them i can write without problems but i cannot use back to go back or up to access the previous command even if i launch vim the arrows are blocked but the hjkl keys work but if i run a command or even ctrl c the arrow keys unfreeze and i can use them i tried running alacritty vv from a terminal to see the debug output but then this freezing doesn t happen i ve tried just alacritty and no freezing system os void linux kernel zsh version linux bsd gaps compton windows pty logs crashes none font terminal size new num cols is and num lines is width height keyboard and bindings key bindings key v mods control shift action paste key c mods control shift action copy key equals mods control action resetfontsize key add mods control action increasefontsize key subtract mods control action decreasefontsize key minus mods control action decreasefontsize edit apparently changing focus using the mod seems to fix the issue but it happens every time i open the terminal | 1 |
173,051 | 14,400,482,659 | IssuesEvent | 2020-12-03 12:26:42 | ocaml/opam | https://api.github.com/repos/ocaml/opam | closed | pin docs incorrectly claims that users can pin from git url | AREA: DOCUMENTATION | # Problem
`opam pin` from git url does not work exactly as described
### Works
The below combo of `opam pin -n ...` + `opam install <pkg>` take:
```
❯ opam pin add -y -n git+http://github.com/EduardoRFS/ocamlearlybird#2e37822
[ocamlearlybird] synchronised from git+http://github.com/EduardoRFS/ocamlearlybird#2e37822
[earlybird.0.1.4] synchronised from git+http://github.com/EduardoRFS/ocamlearlybird#2e37822
earlybird is now pinned to git+http://github.com/EduardoRFS/ocamlearlybird#2e37822 (version 0.1.4)
❯ opam install earlybird
# ok
```
### Fails
However, the below fail, seemingly in contrast to https://opam.ocaml.org/doc/Usage.html#opam-pin .
`opam pin add <pkg> <url>#<commit>`:
```
❯ opam pin add earlybird http://github.com/EduardoRFS/ocamlearlybird#2e37822
[earlybird.0.1.4] downloaded from http://github.com/EduardoRFS/ocamlearlybird#2e37822
[ERROR] Error getting source from http://github.com/EduardoRFS/ocamlearlybird#2e37822:
- Unknown archive type: /private/var/folders/nx/8ddl3q8d3cq8r89p8m9rt8gc0000gn/T/opam-13735-05296d/ocamlearlybird
```
`opam pin add <pkg> <url-branch>`
```
❯ opam pin https://github.com/EduardoRFS/ocamlearlybird/tree/fold-values-workaround-4.09
[fold-values-workaround-4] downloaded from https://github.com/EduardoRFS/ocamlearlybird/tree/fold-values-workaround-4.09
[ERROR] Could not retrieve Unknown archive type:
/private/var/folders/nx/8ddl3q8d3cq8r89p8m9rt8gc0000gn/T/opam-13246-9b8556/fold-values-workaround-4.09
```
Same as above with `opam pin add <pkg> <url>#<branch>`
`opam pin <url-branch>.git`
```
❯ opam pin https://github.com/EduardoRFS/ocamlearlybird/tree/fold-values-workaround-4.09.git
[ERROR] Could not synchronize
/private/var/folders/nx/8ddl3q8d3cq8r89p8m9rt8gc0000gn/T/opam-pin-cache-13305-5a61c5/2b6cb074ff0fb73e8f0eead2bc854d562a774953287af766c449728ef69332c189d51381e475b4f6ebda042e8b5775ac9112c2a9a13034621de7f68d10d47f1c
from "git+https://github.com/EduardoRFS/ocamlearlybird/tree/fold-values-workaround-4.09.git":
"/usr/local/bin/git fetch -q" exited with code 128 "fatal: repository
'https://github.com/EduardoRFS/ocamlearlybird/tree/fold-values-workaround-4.09.git/' not found"
[ERROR] Could not retrieve git+https://github.com/EduardoRFS/ocamlearlybird/tree/fold-values-workaround-4.09.git
``` | 1.0 | pin docs incorrectly claims that users can pin from git url - # Problem
`opam pin` from git url does not work exactly as described
### Works
The below combo of `opam pin -n ...` + `opam install <pkg>` take:
```
❯ opam pin add -y -n git+http://github.com/EduardoRFS/ocamlearlybird#2e37822
[ocamlearlybird] synchronised from git+http://github.com/EduardoRFS/ocamlearlybird#2e37822
[earlybird.0.1.4] synchronised from git+http://github.com/EduardoRFS/ocamlearlybird#2e37822
earlybird is now pinned to git+http://github.com/EduardoRFS/ocamlearlybird#2e37822 (version 0.1.4)
❯ opam install earlybird
# ok
```
### Fails
However, the below fail, seemingly in contrast to https://opam.ocaml.org/doc/Usage.html#opam-pin .
`opam pin add <pkg> <url>#<commit>`:
```
❯ opam pin add earlybird http://github.com/EduardoRFS/ocamlearlybird#2e37822
[earlybird.0.1.4] downloaded from http://github.com/EduardoRFS/ocamlearlybird#2e37822
[ERROR] Error getting source from http://github.com/EduardoRFS/ocamlearlybird#2e37822:
- Unknown archive type: /private/var/folders/nx/8ddl3q8d3cq8r89p8m9rt8gc0000gn/T/opam-13735-05296d/ocamlearlybird
```
`opam pin add <pkg> <url-branch>`
```
❯ opam pin https://github.com/EduardoRFS/ocamlearlybird/tree/fold-values-workaround-4.09
[fold-values-workaround-4] downloaded from https://github.com/EduardoRFS/ocamlearlybird/tree/fold-values-workaround-4.09
[ERROR] Could not retrieve Unknown archive type:
/private/var/folders/nx/8ddl3q8d3cq8r89p8m9rt8gc0000gn/T/opam-13246-9b8556/fold-values-workaround-4.09
```
Same as above with `opam pin add <pkg> <url>#<branch>`
`opam pin <url-branch>.git`
```
❯ opam pin https://github.com/EduardoRFS/ocamlearlybird/tree/fold-values-workaround-4.09.git
[ERROR] Could not synchronize
/private/var/folders/nx/8ddl3q8d3cq8r89p8m9rt8gc0000gn/T/opam-pin-cache-13305-5a61c5/2b6cb074ff0fb73e8f0eead2bc854d562a774953287af766c449728ef69332c189d51381e475b4f6ebda042e8b5775ac9112c2a9a13034621de7f68d10d47f1c
from "git+https://github.com/EduardoRFS/ocamlearlybird/tree/fold-values-workaround-4.09.git":
"/usr/local/bin/git fetch -q" exited with code 128 "fatal: repository
'https://github.com/EduardoRFS/ocamlearlybird/tree/fold-values-workaround-4.09.git/' not found"
[ERROR] Could not retrieve git+https://github.com/EduardoRFS/ocamlearlybird/tree/fold-values-workaround-4.09.git
``` | non_main | pin docs incorrectly claims that users can pin from git url problem opam pin from git url does not work exactly as described works the below combo of opam pin n opam install take ❯ opam pin add y n git synchronised from git synchronised from git earlybird is now pinned to git version ❯ opam install earlybird ok fails however the below fail seemingly in contrast to opam pin add ❯ opam pin add earlybird downloaded from error getting source from unknown archive type private var folders nx t opam ocamlearlybird opam pin add ❯ opam pin downloaded from could not retrieve unknown archive type private var folders nx t opam fold values workaround same as above with opam pin add opam pin git ❯ opam pin could not synchronize private var folders nx t opam pin cache from git usr local bin git fetch q exited with code fatal repository not found could not retrieve git | 0 |
2,391 | 8,494,883,334 | IssuesEvent | 2018-10-29 01:31:17 | chocolatey/chocolatey-package-requests | https://api.github.com/repos/chocolatey/chocolatey-package-requests | closed | RFP - python.pypy3 | Status: Available For Maintainer(s) | Homepage: <https://www.pypy.org/>
Download link (x32 only): <https://bitbucket.org/pypy/pypy/downloads/pypy3-v6.0.0-win32.zip>
I'm not sure whether it qualifies because it's in beta. Package name is picked to be consistent with <https://chocolatey.org/packages/python.pypy>.
`irm 'https://api.bitbucket.org/2.0/repositories/pypy/pypy/refs/tags?q=name~%22pypy3%22&sort=-target.date'` | True | RFP - python.pypy3 - Homepage: <https://www.pypy.org/>
Download link (x32 only): <https://bitbucket.org/pypy/pypy/downloads/pypy3-v6.0.0-win32.zip>
I'm not sure whether it qualifies because it's in beta. Package name is picked to be consistent with <https://chocolatey.org/packages/python.pypy>.
`irm 'https://api.bitbucket.org/2.0/repositories/pypy/pypy/refs/tags?q=name~%22pypy3%22&sort=-target.date'` | main | rfp python homepage download link only i m not sure whether it qualifies because it s in beta package name is picked to be consistent with irm | 1 |
5,287 | 26,703,835,508 | IssuesEvent | 2023-01-27 16:25:52 | cosmos/ibc-rs | https://api.github.com/repos/cosmos/ibc-rs | opened | Extract validation step inside new client state creation and expose it as a separate method | O: maintainability O: ADR06 | <!-- < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < ☺
v ✰ Thanks for opening an issue! ✰
v Before smashing the submit button please review the template.
v Please also ensure that this is not a duplicate issue :)
☺ > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > -->
## Improvement Summary
Separate validation from new client state creation method ([here](https://github.com/cosmos/ibc-rs/blob/ef52941e29aa2759e2861cdae8a7398b114cc5f2/crates/ibc/src/clients/ics07_tendermint/client_state.rs#L83))
## Proposal
- Client states received via an IBC message should be verifiable without having to create a new one. There should be a separate `validate()` method exposed to encompass all the fields' validation checks.
- The inclusion of validation steps inside new() may also lead to implementors forgetting to perform validations
- One use case is for upgrading client process. | True | Extract validation step inside new client state creation and expose it as a separate method - <!-- < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < ☺
v ✰ Thanks for opening an issue! ✰
v Before smashing the submit button please review the template.
v Please also ensure that this is not a duplicate issue :)
☺ > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > -->
## Improvement Summary
Separate validation from new client state creation method ([here](https://github.com/cosmos/ibc-rs/blob/ef52941e29aa2759e2861cdae8a7398b114cc5f2/crates/ibc/src/clients/ics07_tendermint/client_state.rs#L83))
## Proposal
- Client states received via an IBC message should be verifiable without having to create a new one. There should be a separate `validate()` method exposed to encompass all the fields' validation checks.
- The inclusion of validation steps inside new() may also lead to implementors forgetting to perform validations
- One use case is for upgrading client process. | main | extract validation step inside new client state creation and expose it as a separate method ☺ v ✰ thanks for opening an issue ✰ v before smashing the submit button please review the template v please also ensure that this is not a duplicate issue ☺ improvement summary separate validation from new client state creation method proposal client states received via an ibc message should be verifiable without having to create a new one there should be a separate validate method exposed to encompass all the fields validation checks the inclusion of validation steps inside new may also lead to implementors forgetting to perform validations one use case is for upgrading client process | 1 |
76,007 | 14,546,989,087 | IssuesEvent | 2020-12-15 22:09:08 | MicrosoftDocs/azure-devops-docs | https://api.github.com/repos/MicrosoftDocs/azure-devops-docs | closed | feature branch naming convention is not consistent | devops-code-git/tech devops/prod doc-enhancement |
[Enter feedback here]
the image and text do not match the image has "feature"
where as the kiss suggestion shows "features"
the topic branching strategy suggestions on this page are not consistent.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: fe168fc3-2ed2-b3e6-ce30-cac721165ceb
* Version Independent ID: 8d63fbd7-12c4-9a94-92f6-969e7eb41037
* Content: [Git branching guidance - Azure Repos](https://docs.microsoft.com/en-us/azure/devops/repos/git/git-branching-guidance?view=azure-devops)
* Content Source: [docs/repos/git/git-branching-guidance.md](https://github.com/MicrosoftDocs/azure-devops-docs/blob/master/docs/repos/git/git-branching-guidance.md)
* Product: **devops**
* Technology: **devops-code-git**
* GitHub Login: @vtbassmatt
* Microsoft Alias: **macoope** | 1.0 | feature branch naming convention is not consistent -
[Enter feedback here]
the image and text do not match the image has "feature"
where as the kiss suggestion shows "features"
the topic branching strategy suggestions on this page are not consistent.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: fe168fc3-2ed2-b3e6-ce30-cac721165ceb
* Version Independent ID: 8d63fbd7-12c4-9a94-92f6-969e7eb41037
* Content: [Git branching guidance - Azure Repos](https://docs.microsoft.com/en-us/azure/devops/repos/git/git-branching-guidance?view=azure-devops)
* Content Source: [docs/repos/git/git-branching-guidance.md](https://github.com/MicrosoftDocs/azure-devops-docs/blob/master/docs/repos/git/git-branching-guidance.md)
* Product: **devops**
* Technology: **devops-code-git**
* GitHub Login: @vtbassmatt
* Microsoft Alias: **macoope** | non_main | feature branch naming convention is not consistent the image and text do not match the image has feature where as the kiss suggestion shows features the topic branching strategy suggestions on this page are not consistent document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source product devops technology devops code git github login vtbassmatt microsoft alias macoope | 0 |
248,637 | 18,858,100,135 | IssuesEvent | 2021-11-12 09:23:07 | swongts/pe | https://api.github.com/repos/swongts/pe | opened | Mealplan badly formatted | severity.Medium type.DocumentationBug | 
Confusing as add /mealplan is not included in meal plan database category. I was very confused about create /mealplan and add /mealplan just from reading the user guide.
<!--session: 1636706288616-8fe8d33d-8717-4876-908c-1a74efc3ad6f-->
<!--Version: Web v3.4.1--> | 1.0 | Mealplan badly formatted - 
Confusing as add /mealplan is not included in meal plan database category. I was very confused about create /mealplan and add /mealplan just from reading the user guide.
<!--session: 1636706288616-8fe8d33d-8717-4876-908c-1a74efc3ad6f-->
<!--Version: Web v3.4.1--> | non_main | mealplan badly formatted confusing as add mealplan is not included in meal plan database category i was very confused about create mealplan and add mealplan just from reading the user guide | 0 |
838 | 4,478,700,039 | IssuesEvent | 2016-08-27 05:29:49 | DynamoRIO/drmemory | https://api.github.com/repos/DynamoRIO/drmemory | closed | support loading syscall numbers from a downloadable text file | Component-DrSyscall Maintainability OpSys-Windows Type-Feature | Split from #1848: this is a simpler solution and serves as incremental progress toward full automation.
The idea is to support loading system call numbers from a text file that we can provide much more easily than we can create a whole new release package. When DrM detects an invalid kernel, it will notify the user with a message "please download http://drmemory.org/syscalls_wow64.txt into c:\...\Dr. Memory\bin\". | True | support loading syscall numbers from a downloadable text file - Split from #1848: this is a simpler solution and serves as incremental progress toward full automation.
The idea is to support loading system call numbers from a text file that we can provide much more easily than we can create a whole new release package. When DrM detects an invalid kernel, it will notify the user with a message "please download http://drmemory.org/syscalls_wow64.txt into c:\...\Dr. Memory\bin\". | main | support loading syscall numbers from a downloadable text file split from this is a simpler solution and serves as incremental progress toward full automation the idea is to support loading system call numbers from a text file that we can provide much more easily than we can create a whole new release package when drm detects an invalid kernel it will notify the user with a message please download into c dr memory bin | 1 |
191 | 2,505,173,333 | IssuesEvent | 2015-01-11 04:52:16 | bitcoin/secp256k1 | https://api.github.com/repos/bitcoin/secp256k1 | opened | Docucmentation should provide example callers. | documentation | We've seen some people attempting to use the library calling into random internal functions. That should be harder to do now... but now that the basic signature interface is relatively safe to use (as such things go) there should be some easy copy and paste examples for correct usage.
| 1.0 | Docucmentation should provide example callers. - We've seen some people attempting to use the library calling into random internal functions. That should be harder to do now... but now that the basic signature interface is relatively safe to use (as such things go) there should be some easy copy and paste examples for correct usage.
| non_main | docucmentation should provide example callers we ve seen some people attempting to use the library calling into random internal functions that should be harder to do now but now that the basic signature interface is relatively safe to use as such things go there should be some easy copy and paste examples for correct usage | 0 |
1,389 | 6,018,220,629 | IssuesEvent | 2017-06-07 11:45:54 | ansible/ansible-modules-extras | https://api.github.com/repos/ansible/ansible-modules-extras | closed | win_package not accepting exit code 3010 as success | affects_2.1 bug_report in progress waiting_on_maintainer windows | ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
win_package
##### ANSIBLE VERSION
<!--- Paste verbatim output from “ansible --version” between quotes below -->
```
ansible 2.1.0.0
config file = /etc/ansible/ansible.cfg
configured module search path = Default w/o overrides
```
##### CONFIGURATION
Default options
##### OS / ENVIRONMENT
Ansible on RHEL 6, deploying to a Windows 2008 R2 server
##### SUMMARY
When installing some msi, the return code is 3010 (requires restart). This is considered as a failed return code instead of a successful return code
##### STEPS TO REPRODUCE
Call the win_package module for an installer that returns exit code 3010 when installing (Visual C++ 2008 redistributable for example)
```
- name: Install Visual C++ 2008 Runtime
win_package:
name: 'Microsoft Visual C++ 2008 Runtime'
path: 'C;\temp\vcredist_x86.exe'
product_id: '{FF66E9F6-83E7-3A3E-AF14-8DE9A809A6A4}'
arguments: '/q'
```
##### EXPECTED RESULTS
The step should be successful and changed as the package was installed. As an example, chocolatey accept several return codes as valid. It could also be implemented by having a new property to list valid return codes.
##### ACTUAL RESULTS
returned json:
{
"_ansible_no_log": false,
"changed": false,
"failed": true,
"msg": "The return code 3010 was not expected. Configuration is likely not correct",
"name": "Microsoft Visual C++ 2008 Runtime",
"play": "Deploy VC++",
"event_loop": null,
"task": "vcredist : Install Visual C++ 2008 Runtime",
"role": "vcredist",
"ignore_errors": null,
"status": "failed",
"module_name": "win_package",
"created": "2016-09-29T13:55:09.750Z",
"host_id": 852,
"host_name": "targetserv",
"id": 101457,
"parent": 101456,
"event": "Host Failed"
}
| True | win_package not accepting exit code 3010 as success - ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
win_package
##### ANSIBLE VERSION
<!--- Paste verbatim output from “ansible --version” between quotes below -->
```
ansible 2.1.0.0
config file = /etc/ansible/ansible.cfg
configured module search path = Default w/o overrides
```
##### CONFIGURATION
Default options
##### OS / ENVIRONMENT
Ansible on RHEL 6, deploying to a Windows 2008 R2 server
##### SUMMARY
When installing some msi, the return code is 3010 (requires restart). This is considered as a failed return code instead of a successful return code
##### STEPS TO REPRODUCE
Call the win_package module for an installer that returns exit code 3010 when installing (Visual C++ 2008 redistributable for example)
```
- name: Install Visual C++ 2008 Runtime
win_package:
name: 'Microsoft Visual C++ 2008 Runtime'
path: 'C;\temp\vcredist_x86.exe'
product_id: '{FF66E9F6-83E7-3A3E-AF14-8DE9A809A6A4}'
arguments: '/q'
```
##### EXPECTED RESULTS
The step should be successful and changed as the package was installed. As an example, chocolatey accept several return codes as valid. It could also be implemented by having a new property to list valid return codes.
##### ACTUAL RESULTS
returned json:
{
"_ansible_no_log": false,
"changed": false,
"failed": true,
"msg": "The return code 3010 was not expected. Configuration is likely not correct",
"name": "Microsoft Visual C++ 2008 Runtime",
"play": "Deploy VC++",
"event_loop": null,
"task": "vcredist : Install Visual C++ 2008 Runtime",
"role": "vcredist",
"ignore_errors": null,
"status": "failed",
"module_name": "win_package",
"created": "2016-09-29T13:55:09.750Z",
"host_id": 852,
"host_name": "targetserv",
"id": 101457,
"parent": 101456,
"event": "Host Failed"
}
| main | win package not accepting exit code as success issue type bug report component name win package ansible version ansible config file etc ansible ansible cfg configured module search path default w o overrides configuration default options os environment ansible on rhel deploying to a windows server summary when installing some msi the return code is requires restart this is considered as a failed return code instead of a successful return code steps to reproduce call the win package module for an installer that returns exit code when installing visual c redistributable for example name install visual c runtime win package name microsoft visual c runtime path c temp vcredist exe product id arguments q expected results the step should be successful and changed as the package was installed as an example chocolatey accept several return codes as valid it could also be implemented by having a new property to list valid return codes actual results returned json ansible no log false changed false failed true msg the return code was not expected configuration is likely not correct name microsoft visual c runtime play deploy vc event loop null task vcredist install visual c runtime role vcredist ignore errors null status failed module name win package created host id host name targetserv id parent event host failed | 1 |
4,992 | 25,708,348,563 | IssuesEvent | 2022-12-07 03:31:09 | aws/serverless-application-model | https://api.github.com/repos/aws/serverless-application-model | closed | Secrets manager resolve for VPC endpoint ids in Rest API | area/troubleshooting stage/accepted maintainer/need-followup | **Description:**
We want to be able to configure API Gateway's private endpoint to create a private API. The VPC endpoint IDs are resolved through secrets manager. With CloudFormation, API Gateway supports two properties in [the `EndpointConfiguration` object](https://docs.aws.amazon.com/AWSCloudFormation/latest/UserGuide/aws-properties-apigateway-restapi-endpointconfiguration.html): `Type` and an array of `VpcEndpointIds`. With SAM, [the `EndpointConfiguration` property](https://docs.aws.amazon.com/serverless-application-model/latest/developerguide/sam-resource-api.html#sam-api-endpointconfiguration) is a string and only supports the equivalent of the `Type` property in CloudFormation. Further, the template fails validation with SAM when we use the `{{resolve:ssm:...}}` syntax for the `EndpointConfiguration`.
**Steps to reproduce the issue:**
```yaml
EndpointConfiguration:
Types: PRIVATE
VpcEndpointIds=["{{resolve:ssm:vpcprivatelink-api_gateway-private_vpc_endpoint_id:1}}"]
```
**Observed result:**
**Expected result:**
| True | Secrets manager resolve for VPC endpoint ids in Rest API - **Description:**
We want to be able to configure API Gateway's private endpoint to create a private API. The VPC endpoint IDs are resolved through secrets manager. With CloudFormation, API Gateway supports two properties in [the `EndpointConfiguration` object](https://docs.aws.amazon.com/AWSCloudFormation/latest/UserGuide/aws-properties-apigateway-restapi-endpointconfiguration.html): `Type` and an array of `VpcEndpointIds`. With SAM, [the `EndpointConfiguration` property](https://docs.aws.amazon.com/serverless-application-model/latest/developerguide/sam-resource-api.html#sam-api-endpointconfiguration) is a string and only supports the equivalent of the `Type` property in CloudFormation. Further, the template fails validation with SAM when we use the `{{resolve:ssm:...}}` syntax for the `EndpointConfiguration`.
**Steps to reproduce the issue:**
```yaml
EndpointConfiguration:
Types: PRIVATE
VpcEndpointIds=["{{resolve:ssm:vpcprivatelink-api_gateway-private_vpc_endpoint_id:1}}"]
```
**Observed result:**
**Expected result:**
| main | secrets manager resolve for vpc endpoint ids in rest api description we want to be able to configure api gateway s private endpoint to create a private api the vpc endpoint ids are resolved through secrets manager with cloudformation api gateway supports two properties in type and an array of vpcendpointids with sam is a string and only supports the equivalent of the type property in cloudformation further the template fails validation with sam when we use the resolve ssm syntax for the endpointconfiguration steps to reproduce the issue yaml endpointconfiguration types private vpcendpointids observed result expected result | 1 |
1,803 | 6,575,924,513 | IssuesEvent | 2017-09-11 17:51:19 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | Nodes Unreachable after Increasing Forks and File Descriptors ansible 2.1.0.0 | affects_2.1 bug_report waiting_on_maintainer | <!--- Verify first that your issue/request is not already reported in GitHub -->
##### ISSUE TYPE
<!--- Pick one below and delete the rest: -->
- Bug Report
##### COMPONENT NAME
<!--- Forks -->
##### ANSIBLE VERSION
<!--- Paste verbatim output from “ansible --version” between quotes below -->
```
ansible 2.1.0.0
config file = /home/jenkins/workspace/keys-test/stack_info/ansiblehosts/ansible.cfg
configured module search path = Default w/o overrides
```
##### CONFIGURATION
added forks=13 in ansible.cfg increased File descriptors to 8192
##### OS / ENVIRONMENT
ubuntu 14.04 (From and managed)
##### SUMMARY
We Increased the number of forks from default 5 to 20 and for that we increased the File Descriptors (hard and soft limit to 8192) But we have been seeing intermittent failures. 2 out of three times the job goes through successfully, also by decreasing the number of forks we dont see failures. With forks 11 or higher we see intermittent failures. There might be a file descriptor leak. Please advise-
##### STEPS TO REPRODUCE
added forks=13 under [defaults] and ran a sample playbook that runs a simple command on the managed nodes
<!--- Paste example playbooks or commands between quotes below -->
```
ansible-playbook -vvvv -i /home/jenkins/workspace/keys-test/stack_info/ansiblehosts/hosts/hosts_all.ini /home/jenkins/workspace/keys-test/test.yml
- hosts:
- cassandra_node_*
- analytic_node_*
- analytic2_node_1
- solr_node_*
user: ubuntu
sudo: yes
tasks:
- name: Test Ansible Connection
command: ls /home/ubuntu
~
```
<!--- You can also paste gist.github.com links for larger files -->
##### EXPECTED RESULTS
All hosts should be reachable
##### ACTUAL RESULTS
2 hosts unreachable
<!--- Paste verbatim command output between quotes below -->
```
18:12:02 <10.xx.xx.xx> ESTABLISH SSH CONNECTION FOR USER: ubuntu
18:12:02 <10.xx.xx.xx> SSH: EXEC ssh -C -vvv -o ControlPersist=15m -F ssh.config -q -o KbdInteractiveAuthentication=no -o PreferredAuthentications=gssapi-with-mic,gssapi-keyex,hostbased,publickey -o PasswordAuthentication=no -o User=ubuntu -o ConnectTimeout=10 -o 'ControlPath=~/.ssh/mux-%r@%h:%p' 10.xx.xx.xx '/bin/sh -c '"'"'( umask 77 && mkdir -p "` echo $HOME/.ansible/tmp/ansible-tmp-1474049522.59-107361301033999 `" && echo ansible-tmp-1474049522.59-107361301033999="` echo $HOME/.ansible/tmp/ansible-tmp-1474049522.59-107361301033999 `" ) && sleep 0'"'"''
18:12:02 fatal: [10.26.41.4]: UNREACHABLE! => {"changed": false, "msg": "Failed to connect to the host via ssh.", "unreachable": true}
18:12:02 <10.xx.xx.xx> ESTABLISH SSH CONNECTION FOR USER: ubuntu
18:12:02 <10.xx.xx.xx> SSH: EXEC ssh -C -vvv -o ControlPersist=15m -F ssh.config -q -o KbdInteractiveAuthentication=no -o PreferredAuthentications=gssapi-with-mic,gssapi-keyex,hostbased,publickey -o PasswordAuthentication=no -o User=ubuntu -o ConnectTimeout=10 -o 'ControlPath=~/.ssh/mux-%r@%h:%p' 10.xx.xx.xx '/bin/sh -c '"'"'( umask 77 && mkdir -p "` echo $HOME/.ansible/tmp/ansible-tmp-1474049522.84-214871160776213 `" && echo ansible-tmp-1474049522.84-214871160776213="` echo $HOME/.ansible/tmp/ansible-tmp-1474049522.84-214871160776213 `" ) && sleep 0'"'"''
18:12:03 fatal: [10.xx.xx.xx]: UNREACHABLE! => {"changed": false, "msg": "Failed to connect to the host via ssh.", "unreachable":
```
| True | Nodes Unreachable after Increasing Forks and File Descriptors ansible 2.1.0.0 - <!--- Verify first that your issue/request is not already reported in GitHub -->
##### ISSUE TYPE
<!--- Pick one below and delete the rest: -->
- Bug Report
##### COMPONENT NAME
<!--- Forks -->
##### ANSIBLE VERSION
<!--- Paste verbatim output from “ansible --version” between quotes below -->
```
ansible 2.1.0.0
config file = /home/jenkins/workspace/keys-test/stack_info/ansiblehosts/ansible.cfg
configured module search path = Default w/o overrides
```
##### CONFIGURATION
added forks=13 in ansible.cfg increased File descriptors to 8192
##### OS / ENVIRONMENT
ubuntu 14.04 (From and managed)
##### SUMMARY
We Increased the number of forks from default 5 to 20 and for that we increased the File Descriptors (hard and soft limit to 8192) But we have been seeing intermittent failures. 2 out of three times the job goes through successfully, also by decreasing the number of forks we dont see failures. With forks 11 or higher we see intermittent failures. There might be a file descriptor leak. Please advise-
##### STEPS TO REPRODUCE
added forks=13 under [defaults] and ran a sample playbook that runs a simple command on the managed nodes
<!--- Paste example playbooks or commands between quotes below -->
```
ansible-playbook -vvvv -i /home/jenkins/workspace/keys-test/stack_info/ansiblehosts/hosts/hosts_all.ini /home/jenkins/workspace/keys-test/test.yml
- hosts:
- cassandra_node_*
- analytic_node_*
- analytic2_node_1
- solr_node_*
user: ubuntu
sudo: yes
tasks:
- name: Test Ansible Connection
command: ls /home/ubuntu
~
```
<!--- You can also paste gist.github.com links for larger files -->
##### EXPECTED RESULTS
All hosts should be reachable
##### ACTUAL RESULTS
2 hosts unreachable
<!--- Paste verbatim command output between quotes below -->
```
18:12:02 <10.xx.xx.xx> ESTABLISH SSH CONNECTION FOR USER: ubuntu
18:12:02 <10.xx.xx.xx> SSH: EXEC ssh -C -vvv -o ControlPersist=15m -F ssh.config -q -o KbdInteractiveAuthentication=no -o PreferredAuthentications=gssapi-with-mic,gssapi-keyex,hostbased,publickey -o PasswordAuthentication=no -o User=ubuntu -o ConnectTimeout=10 -o 'ControlPath=~/.ssh/mux-%r@%h:%p' 10.xx.xx.xx '/bin/sh -c '"'"'( umask 77 && mkdir -p "` echo $HOME/.ansible/tmp/ansible-tmp-1474049522.59-107361301033999 `" && echo ansible-tmp-1474049522.59-107361301033999="` echo $HOME/.ansible/tmp/ansible-tmp-1474049522.59-107361301033999 `" ) && sleep 0'"'"''
18:12:02 fatal: [10.26.41.4]: UNREACHABLE! => {"changed": false, "msg": "Failed to connect to the host via ssh.", "unreachable": true}
18:12:02 <10.xx.xx.xx> ESTABLISH SSH CONNECTION FOR USER: ubuntu
18:12:02 <10.xx.xx.xx> SSH: EXEC ssh -C -vvv -o ControlPersist=15m -F ssh.config -q -o KbdInteractiveAuthentication=no -o PreferredAuthentications=gssapi-with-mic,gssapi-keyex,hostbased,publickey -o PasswordAuthentication=no -o User=ubuntu -o ConnectTimeout=10 -o 'ControlPath=~/.ssh/mux-%r@%h:%p' 10.xx.xx.xx '/bin/sh -c '"'"'( umask 77 && mkdir -p "` echo $HOME/.ansible/tmp/ansible-tmp-1474049522.84-214871160776213 `" && echo ansible-tmp-1474049522.84-214871160776213="` echo $HOME/.ansible/tmp/ansible-tmp-1474049522.84-214871160776213 `" ) && sleep 0'"'"''
18:12:03 fatal: [10.xx.xx.xx]: UNREACHABLE! => {"changed": false, "msg": "Failed to connect to the host via ssh.", "unreachable":
```
| main | nodes unreachable after increasing forks and file descriptors ansible issue type bug report component name ansible version ansible config file home jenkins workspace keys test stack info ansiblehosts ansible cfg configured module search path default w o overrides configuration added forks in ansible cfg increased file descriptors to os environment ubuntu from and managed summary we increased the number of forks from default to and for that we increased the file descriptors hard and soft limit to but we have been seeing intermittent failures out of three times the job goes through successfully also by decreasing the number of forks we dont see failures with forks or higher we see intermittent failures there might be a file descriptor leak please advise steps to reproduce added forks under and ran a sample playbook that runs a simple command on the managed nodes ansible playbook vvvv i home jenkins workspace keys test stack info ansiblehosts hosts hosts all ini home jenkins workspace keys test test yml hosts cassandra node analytic node node solr node user ubuntu sudo yes tasks name test ansible connection command ls home ubuntu expected results all hosts should be reachable actual results hosts unreachable establish ssh connection for user ubuntu ssh exec ssh c vvv o controlpersist f ssh config q o kbdinteractiveauthentication no o preferredauthentications gssapi with mic gssapi keyex hostbased publickey o passwordauthentication no o user ubuntu o connecttimeout o controlpath ssh mux r h p xx xx xx bin sh c umask mkdir p echo home ansible tmp ansible tmp echo ansible tmp echo home ansible tmp ansible tmp sleep fatal unreachable changed false msg failed to connect to the host via ssh unreachable true establish ssh connection for user ubuntu ssh exec ssh c vvv o controlpersist f ssh config q o kbdinteractiveauthentication no o preferredauthentications gssapi with mic gssapi keyex hostbased publickey o passwordauthentication no o user ubuntu o connecttimeout o controlpath ssh mux r h p xx xx xx bin sh c umask mkdir p echo home ansible tmp ansible tmp echo ansible tmp echo home ansible tmp ansible tmp sleep fatal unreachable changed false msg failed to connect to the host via ssh unreachable | 1 |
788,079 | 27,742,527,655 | IssuesEvent | 2023-03-15 15:07:32 | workcraft/workcraft | https://api.github.com/repos/workcraft/workcraft | opened | Support for Workcraft distribution bundled with JVM | enhancement tag:core tag:script priority:high status:confirmed | - [ ] Modify runner scripts to use bundled JVM as the first priority (if it is present in `jre` directory of Workcraft installation)
- [ ] Provide a way to suppress the use of bundled JVM and fall back to native Java installation (if `WORKCRAFT_USE_NATIVE_JAVA` environment variable is set)
- [ ] Report the used JVM version and path (in Console output and About dialog)
- [ ] Extend Workcraft version info with the _edition_ details (if present in `release` file, similar to Java distributions) | 1.0 | Support for Workcraft distribution bundled with JVM - - [ ] Modify runner scripts to use bundled JVM as the first priority (if it is present in `jre` directory of Workcraft installation)
- [ ] Provide a way to suppress the use of bundled JVM and fall back to native Java installation (if `WORKCRAFT_USE_NATIVE_JAVA` environment variable is set)
- [ ] Report the used JVM version and path (in Console output and About dialog)
- [ ] Extend Workcraft version info with the _edition_ details (if present in `release` file, similar to Java distributions) | non_main | support for workcraft distribution bundled with jvm modify runner scripts to use bundled jvm as the first priority if it is present in jre directory of workcraft installation provide a way to suppress the use of bundled jvm and fall back to native java installation if workcraft use native java environment variable is set report the used jvm version and path in console output and about dialog extend workcraft version info with the edition details if present in release file similar to java distributions | 0 |
61,051 | 3,137,545,938 | IssuesEvent | 2015-09-11 03:46:19 | phetsims/tasks | https://api.github.com/repos/phetsims/tasks | closed | Review the accessibility proposed API | High Priority | @jonathanolson requested @samreid to review the accessibility API proposal in https://github.com/phetsims/scenery/issues/461
I'd love to take a look but not sure if I'll be able to look this week or next. | 1.0 | Review the accessibility proposed API - @jonathanolson requested @samreid to review the accessibility API proposal in https://github.com/phetsims/scenery/issues/461
I'd love to take a look but not sure if I'll be able to look this week or next. | non_main | review the accessibility proposed api jonathanolson requested samreid to review the accessibility api proposal in i d love to take a look but not sure if i ll be able to look this week or next | 0 |
2,124 | 7,260,274,220 | IssuesEvent | 2018-02-18 07:28:20 | dgets/DANT2a | https://api.github.com/repos/dgets/DANT2a | closed | Figure out how to restore develop | help wanted maintainability question | Develop got hosed by something I did in the latest merge. Not sure what it was (obviously, or I would've caught the issue), but it breaks the countdown. Anyway, _develop_ just needs to be a copy of _master_ at this point, and everything will be solved. | True | Figure out how to restore develop - Develop got hosed by something I did in the latest merge. Not sure what it was (obviously, or I would've caught the issue), but it breaks the countdown. Anyway, _develop_ just needs to be a copy of _master_ at this point, and everything will be solved. | main | figure out how to restore develop develop got hosed by something i did in the latest merge not sure what it was obviously or i would ve caught the issue but it breaks the countdown anyway develop just needs to be a copy of master at this point and everything will be solved | 1 |
3,044 | 11,303,599,001 | IssuesEvent | 2020-01-17 20:32:04 | backdrop-ops/contrib | https://api.github.com/repos/backdrop-ops/contrib | opened | Application to join: ericfg | Maintainer application | Hello and welcome to the contrib application process! We're happy to have you :)
Before we begin, please note these 3 requirements for new contrib projects:
- [ ] Include a README.md file containing license and maintainer information.
- [ ] Include a LICENSE.txt file.
- [ ] If porting a Drupal 7 project, Maintain the Git history from Drupal.
When your project meets those three criteria, please continue with the following:
**The name of your module, theme, or layout**
No Current Pass
**(Optional) Post a link here to an issue in the drupal.org queue notifying Drupal 7 maintainers that you are working on a Backdrop port of their project**
https://www.drupal.org/project/nocurrent_pass/issues/3106986
**OR (option #2) If you have contributed code to Backdrop core/contrib projects please provide links to pull requests/commits**
**OR (option #3) If you do not intend to contribute code, but would like to update documentation, manage issue queues, etc, please tag an existing contrib group member so they can post their recommendation**
[@USERNAME]
**If you have chosen option #3 above, do you agree to undergo the same review process for coders (above) should you ever decide to contribute code?**
YES
**If you have chosen option #2 or #1 above, do you agree to the [Backdrop Contributed Project Agreement](https://github.com/backdrop-ops/contrib#backdrop-contributed-project-agreement)**
YES
**Post a link to your new Backdrop project under your own GitHub account**
https://github.com/ericfg/nocurrent_pass
Once we have a chance to review your project, we may provide feedback that's meant to be helpful. If everything checks out, you will be invited to the @backdrop-contrib group, and will be able to transfer the project 😉
| True | Application to join: ericfg - Hello and welcome to the contrib application process! We're happy to have you :)
Before we begin, please note these 3 requirements for new contrib projects:
- [ ] Include a README.md file containing license and maintainer information.
- [ ] Include a LICENSE.txt file.
- [ ] If porting a Drupal 7 project, Maintain the Git history from Drupal.
When your project meets those three criteria, please continue with the following:
**The name of your module, theme, or layout**
No Current Pass
**(Optional) Post a link here to an issue in the drupal.org queue notifying Drupal 7 maintainers that you are working on a Backdrop port of their project**
https://www.drupal.org/project/nocurrent_pass/issues/3106986
**OR (option #2) If you have contributed code to Backdrop core/contrib projects please provide links to pull requests/commits**
**OR (option #3) If you do not intend to contribute code, but would like to update documentation, manage issue queues, etc, please tag an existing contrib group member so they can post their recommendation**
[@USERNAME]
**If you have chosen option #3 above, do you agree to undergo the same review process for coders (above) should you ever decide to contribute code?**
YES
**If you have chosen option #2 or #1 above, do you agree to the [Backdrop Contributed Project Agreement](https://github.com/backdrop-ops/contrib#backdrop-contributed-project-agreement)**
YES
**Post a link to your new Backdrop project under your own GitHub account**
https://github.com/ericfg/nocurrent_pass
Once we have a chance to review your project, we may provide feedback that's meant to be helpful. If everything checks out, you will be invited to the @backdrop-contrib group, and will be able to transfer the project 😉
| main | application to join ericfg hello and welcome to the contrib application process we re happy to have you before we begin please note these requirements for new contrib projects include a readme md file containing license and maintainer information include a license txt file if porting a drupal project maintain the git history from drupal when your project meets those three criteria please continue with the following the name of your module theme or layout no current pass optional post a link here to an issue in the drupal org queue notifying drupal maintainers that you are working on a backdrop port of their project or option if you have contributed code to backdrop core contrib projects please provide links to pull requests commits or option if you do not intend to contribute code but would like to update documentation manage issue queues etc please tag an existing contrib group member so they can post their recommendation if you have chosen option above do you agree to undergo the same review process for coders above should you ever decide to contribute code yes if you have chosen option or above do you agree to the yes post a link to your new backdrop project under your own github account once we have a chance to review your project we may provide feedback that s meant to be helpful if everything checks out you will be invited to the backdrop contrib group and will be able to transfer the project 😉 | 1 |
1,038 | 4,832,834,587 | IssuesEvent | 2016-11-08 08:59:42 | ansible/ansible-modules-extras | https://api.github.com/repos/ansible/ansible-modules-extras | closed | Redshift module missing supported machine types in a dictionary | affects_2.3 aws bug_report cloud waiting_on_maintainer | <!--- Verify first that your issue/request is not already reported in GitHub -->
##### ISSUE TYPE
<!--- Pick one below and delete the rest: -->
- Bug Report
##### COMPONENT NAME
<!--- Name of the plugin/module/task -->
ansible/redshift
##### ANSIBLE VERSION
<!--- Paste verbatim output from “ansible --version” between quotes below -->
latest dev branch
##### CONFIGURATION
<!---
Mention any settings you have changed/added/removed in ansible.cfg
(or using the ANSIBLE_* environment variables).
-->
##### OS / ENVIRONMENT
<!---
Mention the OS you are running Ansible from, and the OS you are
managing, or say “N/A” for anything that is not platform-specific.
-->
##### SUMMARY
<!--- Explain the problem briefly -->
Supported machine types in a dictionary are not relevant .
Missing machine type for : 'dc1.large'
##### STEPS TO REPRODUCE
<!---
For bugs, show exactly how to reproduce the problem.
For new features, show how the feature would be used.
-->
<!--- Paste example playbooks or commands between quotes below -->
```
```
<!--- You can also paste gist.github.com links for larger files -->
##### EXPECTED RESULTS
<!--- What did you expect to happen when running the steps above? -->
##### ACTUAL RESULTS
<!--- What actually happened? If possible run with high verbosity (-vvvv) -->
<!--- Paste verbatim command output between quotes below -->
```
```
| True | Redshift module missing supported machine types in a dictionary - <!--- Verify first that your issue/request is not already reported in GitHub -->
##### ISSUE TYPE
<!--- Pick one below and delete the rest: -->
- Bug Report
##### COMPONENT NAME
<!--- Name of the plugin/module/task -->
ansible/redshift
##### ANSIBLE VERSION
<!--- Paste verbatim output from “ansible --version” between quotes below -->
latest dev branch
##### CONFIGURATION
<!---
Mention any settings you have changed/added/removed in ansible.cfg
(or using the ANSIBLE_* environment variables).
-->
##### OS / ENVIRONMENT
<!---
Mention the OS you are running Ansible from, and the OS you are
managing, or say “N/A” for anything that is not platform-specific.
-->
##### SUMMARY
<!--- Explain the problem briefly -->
Supported machine types in a dictionary are not relevant .
Missing machine type for : 'dc1.large'
##### STEPS TO REPRODUCE
<!---
For bugs, show exactly how to reproduce the problem.
For new features, show how the feature would be used.
-->
<!--- Paste example playbooks or commands between quotes below -->
```
```
<!--- You can also paste gist.github.com links for larger files -->
##### EXPECTED RESULTS
<!--- What did you expect to happen when running the steps above? -->
##### ACTUAL RESULTS
<!--- What actually happened? If possible run with high verbosity (-vvvv) -->
<!--- Paste verbatim command output between quotes below -->
```
```
| main | redshift module missing supported machine types in a dictionary issue type bug report component name ansible redshift ansible version latest dev branch configuration mention any settings you have changed added removed in ansible cfg or using the ansible environment variables os environment mention the os you are running ansible from and the os you are managing or say “n a” for anything that is not platform specific summary supported machine types in a dictionary are not relevant missing machine type for large steps to reproduce for bugs show exactly how to reproduce the problem for new features show how the feature would be used expected results actual results | 1 |
201,328 | 7,029,482,219 | IssuesEvent | 2017-12-26 01:22:04 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | olymptrade.com - desktop site instead of mobile site | browser-firefox priority-normal type-stylo | <!-- @browser: Firefox 58.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:58.0) Gecko/20100101 Firefox/58.0 -->
<!-- @reported_with: desktop-reporter -->
<!-- @extra_label: type-stylo -->
**URL**: https://olymptrade.com/en-us/platform
**Browser / Version**: Firefox 58.0
**Operating System**: Windows 10
**Tested Another Browser**: Yes
**Problem type**: Desktop site instead of mobile site
**Description**: my live account doesn't work well. it mean when the i done the trading my bet actuallty to be won but the platform make me lose
**Steps to Reproduce**:
i have record my trading transaction when it almost done till it done and i have comparassion with other trading platform, i think there's a weird on it.
[](https://webcompat.com/uploads/2017/12/79904bf6-43b5-4acb-99d9-a087f238af8b.jpg)
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | olymptrade.com - desktop site instead of mobile site - <!-- @browser: Firefox 58.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:58.0) Gecko/20100101 Firefox/58.0 -->
<!-- @reported_with: desktop-reporter -->
<!-- @extra_label: type-stylo -->
**URL**: https://olymptrade.com/en-us/platform
**Browser / Version**: Firefox 58.0
**Operating System**: Windows 10
**Tested Another Browser**: Yes
**Problem type**: Desktop site instead of mobile site
**Description**: my live account doesn't work well. it mean when the i done the trading my bet actuallty to be won but the platform make me lose
**Steps to Reproduce**:
i have record my trading transaction when it almost done till it done and i have comparassion with other trading platform, i think there's a weird on it.
[](https://webcompat.com/uploads/2017/12/79904bf6-43b5-4acb-99d9-a087f238af8b.jpg)
_From [webcompat.com](https://webcompat.com/) with ❤️_ | non_main | olymptrade com desktop site instead of mobile site url browser version firefox operating system windows tested another browser yes problem type desktop site instead of mobile site description my live account doesn t work well it mean when the i done the trading my bet actuallty to be won but the platform make me lose steps to reproduce i have record my trading transaction when it almost done till it done and i have comparassion with other trading platform i think there s a weird on it from with ❤️ | 0 |
5,147 | 26,239,315,361 | IssuesEvent | 2023-01-05 10:09:08 | OpenRefine/OpenRefine | https://api.github.com/repos/OpenRefine/OpenRefine | closed | Extensions defining new importing controllers need to import theme.less from OpenRefine | bug UI maintainability extension | Some extensions define new "importing controllers" (for instance the gdata and database extension). This is the expected extension point when implementing an importing mechanism which loads data from other sources.
As part of this, extensions need to define parsing pages which look like the importer preview we have in OpenRefine.
For the styling of those parsing pages, both the gdata and database extensions rely on OpenRefine-internal `.less` files that they explicitly import on their own side.
This looks like this:
https://github.com/OpenRefine/OpenRefine/blob/5746951ec069549345eb368ea74a77c3fec9a912/extensions/database/module/styles/theme.less#L30
While this technique avoids duplicating files from the core to the extensions, this is far from ideal because this mechanism is not available to extensions developed outside this repository.
Intuitively, it should be possible for any extension to use the standard styling of the parsing page, without having to redefine it itself. Of course, we still want extensions to be able to add some custom CSS to this page, should they need to.
Ideally, it would be great if we could fix this in a backwards-compatible way (meaning that extensions which have been built for the current situation would keep working with the new system), although this is likely to be difficult. And it is probably not so important since we can easily fix the extensions in this repository.
@antoine2711 @WaltonG this is an issue you are likely to run into (or have already run into?) for the SPARQL extension, no? | True | Extensions defining new importing controllers need to import theme.less from OpenRefine - Some extensions define new "importing controllers" (for instance the gdata and database extension). This is the expected extension point when implementing an importing mechanism which loads data from other sources.
As part of this, extensions need to define parsing pages which look like the importer preview we have in OpenRefine.
For the styling of those parsing pages, both the gdata and database extensions rely on OpenRefine-internal `.less` files that they explicitly import on their own side.
This looks like this:
https://github.com/OpenRefine/OpenRefine/blob/5746951ec069549345eb368ea74a77c3fec9a912/extensions/database/module/styles/theme.less#L30
While this technique avoids duplicating files from the core to the extensions, this is far from ideal because this mechanism is not available to extensions developed outside this repository.
Intuitively, it should be possible for any extension to use the standard styling of the parsing page, without having to redefine it itself. Of course, we still want extensions to be able to add some custom CSS to this page, should they need to.
Ideally, it would be great if we could fix this in a backwards-compatible way (meaning that extensions which have been built for the current situation would keep working with the new system), although this is likely to be difficult. And it is probably not so important since we can easily fix the extensions in this repository.
@antoine2711 @WaltonG this is an issue you are likely to run into (or have already run into?) for the SPARQL extension, no? | main | extensions defining new importing controllers need to import theme less from openrefine some extensions define new importing controllers for instance the gdata and database extension this is the expected extension point when implementing an importing mechanism which loads data from other sources as part of this extensions need to define parsing pages which look like the importer preview we have in openrefine for the styling of those parsing pages both the gdata and database extensions rely on openrefine internal less files that they explicitly import on their own side this looks like this while this technique avoids duplicating files from the core to the extensions this is far from ideal because this mechanism is not available to extensions developed outside this repository intuitively it should be possible for any extension to use the standard styling of the parsing page without having to redefine it itself of course we still want extensions to be able to add some custom css to this page should they need to ideally it would be great if we could fix this in a backwards compatible way meaning that extensions which have been built for the current situation would keep working with the new system although this is likely to be difficult and it is probably not so important since we can easily fix the extensions in this repository waltong this is an issue you are likely to run into or have already run into for the sparql extension no | 1 |
311,650 | 9,537,095,893 | IssuesEvent | 2019-04-30 11:34:21 | kubermatic/kubeone | https://api.github.com/repos/kubermatic/kubeone | closed | Installer waits for machine-controller even if it's disabled | lifecycle/active priority/important-soon | The installer waits for `machine-controller` even if it's not deployed. | 1.0 | Installer waits for machine-controller even if it's disabled - The installer waits for `machine-controller` even if it's not deployed. | non_main | installer waits for machine controller even if it s disabled the installer waits for machine controller even if it s not deployed | 0 |
166,415 | 20,718,493,887 | IssuesEvent | 2022-03-13 01:55:45 | jinuem/node-sass | https://api.github.com/repos/jinuem/node-sass | opened | CVE-2021-32803 (High) detected in tar-2.2.1.tgz | security vulnerability | ## CVE-2021-32803 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-2.2.1.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-2.2.1.tgz">https://registry.npmjs.org/tar/-/tar-2.2.1.tgz</a></p>
<p>Path to dependency file: /node-sass/package.json</p>
<p>Path to vulnerable library: /node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- node-gyp-3.8.0.tgz (Root Library)
- :x: **tar-2.2.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The npm package "tar" (aka node-tar) before versions 6.1.2, 5.0.7, 4.4.15, and 3.2.3 has an arbitrary File Creation/Overwrite vulnerability via insufficient symlink protection. `node-tar` aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary `stat` calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory. This order of operations resulted in the directory being created and added to the `node-tar` directory cache. When a directory is present in the directory cache, subsequent calls to mkdir for that directory are skipped. However, this is also where `node-tar` checks for symlinks occur. By first creating a directory, and then replacing that directory with a symlink, it was thus possible to bypass `node-tar` symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. This issue was addressed in releases 3.2.3, 4.4.15, 5.0.7 and 6.1.2.
<p>Publish Date: 2021-08-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32803>CVE-2021-32803</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-r628-mhmh-qjhw">https://github.com/npm/node-tar/security/advisories/GHSA-r628-mhmh-qjhw</a></p>
<p>Release Date: 2021-08-03</p>
<p>Fix Resolution (tar): 3.2.3</p>
<p>Direct dependency fix Resolution (node-gyp): 4.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-32803 (High) detected in tar-2.2.1.tgz - ## CVE-2021-32803 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-2.2.1.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-2.2.1.tgz">https://registry.npmjs.org/tar/-/tar-2.2.1.tgz</a></p>
<p>Path to dependency file: /node-sass/package.json</p>
<p>Path to vulnerable library: /node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- node-gyp-3.8.0.tgz (Root Library)
- :x: **tar-2.2.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The npm package "tar" (aka node-tar) before versions 6.1.2, 5.0.7, 4.4.15, and 3.2.3 has an arbitrary File Creation/Overwrite vulnerability via insufficient symlink protection. `node-tar` aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary `stat` calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory. This order of operations resulted in the directory being created and added to the `node-tar` directory cache. When a directory is present in the directory cache, subsequent calls to mkdir for that directory are skipped. However, this is also where `node-tar` checks for symlinks occur. By first creating a directory, and then replacing that directory with a symlink, it was thus possible to bypass `node-tar` symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. This issue was addressed in releases 3.2.3, 4.4.15, 5.0.7 and 6.1.2.
<p>Publish Date: 2021-08-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32803>CVE-2021-32803</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-r628-mhmh-qjhw">https://github.com/npm/node-tar/security/advisories/GHSA-r628-mhmh-qjhw</a></p>
<p>Release Date: 2021-08-03</p>
<p>Fix Resolution (tar): 3.2.3</p>
<p>Direct dependency fix Resolution (node-gyp): 4.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_main | cve high detected in tar tgz cve high severity vulnerability vulnerable library tar tgz tar for node library home page a href path to dependency file node sass package json path to vulnerable library node modules tar package json dependency hierarchy node gyp tgz root library x tar tgz vulnerable library vulnerability details the npm package tar aka node tar before versions and has an arbitrary file creation overwrite vulnerability via insufficient symlink protection node tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted this is in part achieved by ensuring that extracted directories are not symlinks additionally in order to prevent unnecessary stat calls to determine whether a given path is a directory paths are cached when directories are created this logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory this order of operations resulted in the directory being created and added to the node tar directory cache when a directory is present in the directory cache subsequent calls to mkdir for that directory are skipped however this is also where node tar checks for symlinks occur by first creating a directory and then replacing that directory with a symlink it was thus possible to bypass node tar symlink checks on directories essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location thus allowing arbitrary file creation and overwrite this issue was addressed in releases and publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tar direct dependency fix resolution node gyp step up your open source security game with whitesource | 0 |
209,653 | 7,178,343,281 | IssuesEvent | 2018-01-31 16:14:14 | Rubicon-Bot/Rubicon | https://api.github.com/repos/Rubicon-Bot/Rubicon | closed | verification kick | bug high priority | ## Issue
### Issue Type
- [x] Bug.
- [ ] Feature.
### Report
#### Description
When the Bot goes offline until a User got kicked he will never get Kicked
### Steps to reproduce
>Leave Blank if this is a Feature Request
- Step 1
- Stop Bot
- Step 2
- Kick won't work after restart
| 1.0 | verification kick - ## Issue
### Issue Type
- [x] Bug.
- [ ] Feature.
### Report
#### Description
When the Bot goes offline until a User got kicked he will never get Kicked
### Steps to reproduce
>Leave Blank if this is a Feature Request
- Step 1
- Stop Bot
- Step 2
- Kick won't work after restart
| non_main | verification kick issue issue type bug feature report description when the bot goes offline until a user got kicked he will never get kicked steps to reproduce leave blank if this is a feature request step stop bot step kick won t work after restart | 0 |
2,625 | 8,915,238,016 | IssuesEvent | 2019-01-19 03:20:19 | ansible/ansible | https://api.github.com/repos/ansible/ansible | closed | Add the "name" parameter in logentries follow module | feature module needs_maintainer support:community | From @mechastorm on 2014-10-16T21:07:04Z
##### Issue Type:
“Feature Idea”
##### Component Name:
logentries module
##### Summary:
In the current module [logentries ](http://docs.ansible.com/logentries_module.html), it will only accept the `path` parameter to following logs.
In logentries CLI agent, you can now add in a `name` parameter to name your
``` shell
$ le follow '/var/log/nginx*.log' --name="nginx_logs"
```
##### Steps To Reproduce:
when we do
```
- logentries: path=/var/log/nginx*.log state=present
```
On logentries, it defaults the name of this tracking to "_.log" instead for the path `/var/log/nginx_.log`. This makes it slightly confusing and not nice looking (harder to organize).
##### Expected Results:
Propose to add a `name` parameter instead so that we can do
```
- logentries: path=/var/log/nginx*.log state=present name=nginx_logs
```
##### Actual Results:
N/A
Copied from original issue: ansible/ansible-modules-extras#74
| True | Add the "name" parameter in logentries follow module - From @mechastorm on 2014-10-16T21:07:04Z
##### Issue Type:
“Feature Idea”
##### Component Name:
logentries module
##### Summary:
In the current module [logentries ](http://docs.ansible.com/logentries_module.html), it will only accept the `path` parameter to following logs.
In logentries CLI agent, you can now add in a `name` parameter to name your
``` shell
$ le follow '/var/log/nginx*.log' --name="nginx_logs"
```
##### Steps To Reproduce:
when we do
```
- logentries: path=/var/log/nginx*.log state=present
```
On logentries, it defaults the name of this tracking to "_.log" instead for the path `/var/log/nginx_.log`. This makes it slightly confusing and not nice looking (harder to organize).
##### Expected Results:
Propose to add a `name` parameter instead so that we can do
```
- logentries: path=/var/log/nginx*.log state=present name=nginx_logs
```
##### Actual Results:
N/A
Copied from original issue: ansible/ansible-modules-extras#74
| main | add the name parameter in logentries follow module from mechastorm on issue type “feature idea” component name logentries module summary in the current module it will only accept the path parameter to following logs in logentries cli agent you can now add in a name parameter to name your shell le follow var log nginx log name nginx logs steps to reproduce when we do logentries path var log nginx log state present on logentries it defaults the name of this tracking to log instead for the path var log nginx log this makes it slightly confusing and not nice looking harder to organize expected results propose to add a name parameter instead so that we can do logentries path var log nginx log state present name nginx logs actual results n a copied from original issue ansible ansible modules extras | 1 |
1,537 | 6,572,229,186 | IssuesEvent | 2017-09-11 00:20:13 | ansible/ansible-modules-extras | https://api.github.com/repos/ansible/ansible-modules-extras | closed | nmcli: autoconnect not working | affects_2.1 bug_report networking waiting_on_maintainer | ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
nmcli
##### ANSIBLE VERSION
```
# latest head of 2016-04-16
ansible 2.1.0
config file =
configured module search path = Default w/o overrides
```
##### OS / ENVIRONMENT
`CentOS Linux release 7.2.1511 (Core)`
##### SUMMARY
autoconnect not working
##### STEPS TO REPRODUCE
```
- name: Configure network adapter
nmcli: type="ethernet" conn_name="enp0s1" ip4="192.168.1.1/16" ifname="enp0s1" state="present" autoconnect="yes"
```
##### EXPECTED RESULTS
OK
##### ACTUAL RESULTS
FAILED! =>
``` json
{
"rc": 2,
"name": "enp0s1",
"msg": "Error: invalid <setting>.<property> 'autoconnect'.\n",
"invocation": {
"module_name": "nmcli",
"module_args": {
"vlanid": null,
"vlandev": null,
"updelay": null,
"type": "ethernet",
"stp": "yes",
"state": "present",
"slavepriority": "32",
"priority": "128",
"mtu": null,
"mode": "balance-rr",
"miimon": null,
"maxage": "20",
"master": null,
"mac": null,
"ip6": null,
"ip4": "192.168.1.1\/16",
"ingress": null,
"ifname": "enp0s1",
"hellotime": "2",
"gw6": null,
"gw4": null,
"forwarddelay": "15",
"flags": null,
"egress": null,
"downdelay": null,
"dns6": null,
"dns4": null,
"conn_name": "enp0s1",
"autoconnect": "yes",
"arp_ip_target": null,
"arp_interval": null,
"ageingtime": "300"
}
},
"failed": true,
"changed": false
}
```
| True | nmcli: autoconnect not working - ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
nmcli
##### ANSIBLE VERSION
```
# latest head of 2016-04-16
ansible 2.1.0
config file =
configured module search path = Default w/o overrides
```
##### OS / ENVIRONMENT
`CentOS Linux release 7.2.1511 (Core)`
##### SUMMARY
autoconnect not working
##### STEPS TO REPRODUCE
```
- name: Configure network adapter
nmcli: type="ethernet" conn_name="enp0s1" ip4="192.168.1.1/16" ifname="enp0s1" state="present" autoconnect="yes"
```
##### EXPECTED RESULTS
OK
##### ACTUAL RESULTS
FAILED! =>
``` json
{
"rc": 2,
"name": "enp0s1",
"msg": "Error: invalid <setting>.<property> 'autoconnect'.\n",
"invocation": {
"module_name": "nmcli",
"module_args": {
"vlanid": null,
"vlandev": null,
"updelay": null,
"type": "ethernet",
"stp": "yes",
"state": "present",
"slavepriority": "32",
"priority": "128",
"mtu": null,
"mode": "balance-rr",
"miimon": null,
"maxage": "20",
"master": null,
"mac": null,
"ip6": null,
"ip4": "192.168.1.1\/16",
"ingress": null,
"ifname": "enp0s1",
"hellotime": "2",
"gw6": null,
"gw4": null,
"forwarddelay": "15",
"flags": null,
"egress": null,
"downdelay": null,
"dns6": null,
"dns4": null,
"conn_name": "enp0s1",
"autoconnect": "yes",
"arp_ip_target": null,
"arp_interval": null,
"ageingtime": "300"
}
},
"failed": true,
"changed": false
}
```
| main | nmcli autoconnect not working issue type bug report component name nmcli ansible version latest head of ansible config file configured module search path default w o overrides os environment centos linux release core summary autoconnect not working steps to reproduce name configure network adapter nmcli type ethernet conn name ifname state present autoconnect yes expected results ok actual results failed json rc name msg error invalid autoconnect n invocation module name nmcli module args vlanid null vlandev null updelay null type ethernet stp yes state present slavepriority priority mtu null mode balance rr miimon null maxage master null mac null null ingress null ifname hellotime null null forwarddelay flags null egress null downdelay null null null conn name autoconnect yes arp ip target null arp interval null ageingtime failed true changed false | 1 |
416 | 3,486,836,409 | IssuesEvent | 2016-01-01 04:16:22 | noam-c/EDEn | https://api.github.com/repos/noam-c/EDEn | closed | Convert TODOLIST.h into GitHub issues | Maintainability | Several issues are expressed in the TODOLIST.h file, which is an uncompiled C++ file full of comments that can be parsed as a to-do list by Doxygen. It's important to move these issues into a proper issue tracker and add any additional details possible so that they can be picked up and addressed easily. | True | Convert TODOLIST.h into GitHub issues - Several issues are expressed in the TODOLIST.h file, which is an uncompiled C++ file full of comments that can be parsed as a to-do list by Doxygen. It's important to move these issues into a proper issue tracker and add any additional details possible so that they can be picked up and addressed easily. | main | convert todolist h into github issues several issues are expressed in the todolist h file which is an uncompiled c file full of comments that can be parsed as a to do list by doxygen it s important to move these issues into a proper issue tracker and add any additional details possible so that they can be picked up and addressed easily | 1 |
3,114 | 11,904,316,663 | IssuesEvent | 2020-03-30 16:39:04 | diofant/diofant | https://api.github.com/repos/diofant/diofant | opened | Port factorization algorithms to use sparse polys | enhancement maintainability polys | That include implementing factor_list and is_cyclotomic property per [TODO](https://github.com/diofant/diofant/blob/987094a0a22b101e545e291af5ee9f526233f279/diofant/polys/rings.py#L2058-L2059). | True | Port factorization algorithms to use sparse polys - That include implementing factor_list and is_cyclotomic property per [TODO](https://github.com/diofant/diofant/blob/987094a0a22b101e545e291af5ee9f526233f279/diofant/polys/rings.py#L2058-L2059). | main | port factorization algorithms to use sparse polys that include implementing factor list and is cyclotomic property per | 1 |
17,231 | 22,919,495,955 | IssuesEvent | 2022-07-17 12:58:38 | nodejs/security-wg | https://api.github.com/repos/nodejs/security-wg | closed | Node+Interactive Security WG Agenda | process | Let's use this issue to track all the suggestions and recommended agenda for Security WG in upcoming Collab Summit in Node+Interactive Montreal.
-- Update 13/12/2019
Participants: @lirantal @ChALkeR @vdeturckheim
Working Items and Discussions:
1. Bug Bounty Criteria - agreed and confirmed on current guidelines that we've set via https://github.com/nodejs/security-wg/pull/603 , https://github.com/nodejs/security-wg/issues/593 and https://github.com/nodejs/security-wg/issues/525
2. Buckets and Prioritization - we are thinking that the current bucket order helps and a step in a good direction but we want to further improve it. Right now we have 2 buckets: `Low priority <100 d/l weekly` and `High priority >100 d/l weekly` and current stats are 30 vs 36 respectively. So it helps, but we'd like to also make sure we don't starve the reports in >100 that are affecting a good part of the ecosystem (i.e: >100000 downloads). To be discussed in https://github.com/nodejs/security-wg/issues/604
3. Membership activity / On-boarding Program - discussed that many triage group members are existing but not all are actively participating which doesn't improve our state of items in the queue for triage. Related to this topic, we discussed perhaps creating an on-boarding program where we would have members rotating for a 3-6 months on and off the triage team, since we the work can be burning out for most people, and also have a program where members start off with low priority buckets to help them grow with experience and into the "way of things" and then transition to one of the other higher priority buckets.
| 1.0 | Node+Interactive Security WG Agenda - Let's use this issue to track all the suggestions and recommended agenda for Security WG in upcoming Collab Summit in Node+Interactive Montreal.
-- Update 13/12/2019
Participants: @lirantal @ChALkeR @vdeturckheim
Working Items and Discussions:
1. Bug Bounty Criteria - agreed and confirmed on current guidelines that we've set via https://github.com/nodejs/security-wg/pull/603 , https://github.com/nodejs/security-wg/issues/593 and https://github.com/nodejs/security-wg/issues/525
2. Buckets and Prioritization - we are thinking that the current bucket order helps and a step in a good direction but we want to further improve it. Right now we have 2 buckets: `Low priority <100 d/l weekly` and `High priority >100 d/l weekly` and current stats are 30 vs 36 respectively. So it helps, but we'd like to also make sure we don't starve the reports in >100 that are affecting a good part of the ecosystem (i.e: >100000 downloads). To be discussed in https://github.com/nodejs/security-wg/issues/604
3. Membership activity / On-boarding Program - discussed that many triage group members are existing but not all are actively participating which doesn't improve our state of items in the queue for triage. Related to this topic, we discussed perhaps creating an on-boarding program where we would have members rotating for a 3-6 months on and off the triage team, since we the work can be burning out for most people, and also have a program where members start off with low priority buckets to help them grow with experience and into the "way of things" and then transition to one of the other higher priority buckets.
| non_main | node interactive security wg agenda let s use this issue to track all the suggestions and recommended agenda for security wg in upcoming collab summit in node interactive montreal update participants lirantal chalker vdeturckheim working items and discussions bug bounty criteria agreed and confirmed on current guidelines that we ve set via and buckets and prioritization we are thinking that the current bucket order helps and a step in a good direction but we want to further improve it right now we have buckets low priority d l weekly and current stats are vs respectively so it helps but we d like to also make sure we don t starve the reports in that are affecting a good part of the ecosystem i e downloads to be discussed in membership activity on boarding program discussed that many triage group members are existing but not all are actively participating which doesn t improve our state of items in the queue for triage related to this topic we discussed perhaps creating an on boarding program where we would have members rotating for a months on and off the triage team since we the work can be burning out for most people and also have a program where members start off with low priority buckets to help them grow with experience and into the way of things and then transition to one of the other higher priority buckets | 0 |
671,759 | 22,774,932,661 | IssuesEvent | 2022-07-08 13:38:28 | opensquare-network/paid-qa | https://api.github.com/repos/opensquare-network/paid-qa | closed | refactor: don't use sub-component directly | UI priority:low | e.g.
- Don't use `MicromarkMd`, use `Preview`
- Don't use `MarkdownEditor`, use `RichEditor`
- Don't use `Dropdown(item)` and write a new Selector, use `DropdownSelector`
Sub-components is **not** for public.
If so, we'll have bulk of work to do/refactor. | 1.0 | refactor: don't use sub-component directly - e.g.
- Don't use `MicromarkMd`, use `Preview`
- Don't use `MarkdownEditor`, use `RichEditor`
- Don't use `Dropdown(item)` and write a new Selector, use `DropdownSelector`
Sub-components is **not** for public.
If so, we'll have bulk of work to do/refactor. | non_main | refactor don t use sub component directly e g don t use micromarkmd use preview don t use markdowneditor use richeditor don t use dropdown item and write a new selector use dropdownselector sub components is not for public if so we ll have bulk of work to do refactor | 0 |
1,556 | 6,572,249,617 | IssuesEvent | 2017-09-11 00:36:01 | ansible/ansible-modules-extras | https://api.github.com/repos/ansible/ansible-modules-extras | closed | Support large number of services on ecs_service_facts | affects_2.1 aws bug_report cloud waiting_on_maintainer | <!--- Verify first that your issue/request is not already reported in GitHub -->
##### ISSUE TYPE
<!--- Pick one below and delete the rest: -->
- Bug Report
##### COMPONENT NAME
ecs_service_facts
##### ANSIBLE VERSION
<!--- Paste verbatim output from “ansible --version” between quotes below -->
2.1.0
##### OS / ENVIRONMENT
N/A
##### SUMMARY
Support for more than 10 services on a cluster
##### STEPS TO REPRODUCE
<!--- Paste example playbooks or commands between quotes below -->
```
# List on services on ECS
- ecs_service_facts:
cluster: cluster_name
register: ECS
- debug: var=ECS
```
Only 10 service are listed while we have about 60 services
<!--- You can also paste gist.github.com links for larger files -->
##### EXPECTED RESULTS
Get full list of services
##### ACTUAL RESULTS
<!--- What actually happened? If possible run with high verbosity (-vvvv) -->
ok: [localhost] => {
"ECS": {
"ansible_facts": {
"services": [
"arn:aws:ecs:us-east-1:123456780123:service/clustername_import-xxx",
"arn:aws:ecs:us-east-1:123456780123:service/clustername_logistic-aaa-event",
"arn:aws:ecs:us-east-1:123456780123:service/clustername_test-mapping",
"arn:aws:ecs:us-east-1:123456780123:service/clustername_consumer-xxx",
"arn:aws:ecs:us-east-1:123456780123:service/clustername_searcr",
"arn:aws:ecs:us-east-1:123456780123:service/clustername_sales-test-aaa",
"arn:aws:ecs:us-east-1:123456780123:service/clustername_sales-test-ggg",
"arn:aws:ecs:us-east-1:123456780123:service/clustername_price-test",
"arn:aws:ecs:us-east-1:123456780123:service/clustername_shipment-test",
"arn:aws:ecs:us-east-1:123456780123:service/clustername_test3"
]
},
"changed": false
}
}
<!--- Paste verbatim command output between quotes below -->
```
```
| True | Support large number of services on ecs_service_facts - <!--- Verify first that your issue/request is not already reported in GitHub -->
##### ISSUE TYPE
<!--- Pick one below and delete the rest: -->
- Bug Report
##### COMPONENT NAME
ecs_service_facts
##### ANSIBLE VERSION
<!--- Paste verbatim output from “ansible --version” between quotes below -->
2.1.0
##### OS / ENVIRONMENT
N/A
##### SUMMARY
Support for more than 10 services on a cluster
##### STEPS TO REPRODUCE
<!--- Paste example playbooks or commands between quotes below -->
```
# List on services on ECS
- ecs_service_facts:
cluster: cluster_name
register: ECS
- debug: var=ECS
```
Only 10 service are listed while we have about 60 services
<!--- You can also paste gist.github.com links for larger files -->
##### EXPECTED RESULTS
Get full list of services
##### ACTUAL RESULTS
<!--- What actually happened? If possible run with high verbosity (-vvvv) -->
ok: [localhost] => {
"ECS": {
"ansible_facts": {
"services": [
"arn:aws:ecs:us-east-1:123456780123:service/clustername_import-xxx",
"arn:aws:ecs:us-east-1:123456780123:service/clustername_logistic-aaa-event",
"arn:aws:ecs:us-east-1:123456780123:service/clustername_test-mapping",
"arn:aws:ecs:us-east-1:123456780123:service/clustername_consumer-xxx",
"arn:aws:ecs:us-east-1:123456780123:service/clustername_searcr",
"arn:aws:ecs:us-east-1:123456780123:service/clustername_sales-test-aaa",
"arn:aws:ecs:us-east-1:123456780123:service/clustername_sales-test-ggg",
"arn:aws:ecs:us-east-1:123456780123:service/clustername_price-test",
"arn:aws:ecs:us-east-1:123456780123:service/clustername_shipment-test",
"arn:aws:ecs:us-east-1:123456780123:service/clustername_test3"
]
},
"changed": false
}
}
<!--- Paste verbatim command output between quotes below -->
```
```
| main | support large number of services on ecs service facts issue type bug report component name ecs service facts ansible version os environment n a summary support for more than services on a cluster steps to reproduce list on services on ecs ecs service facts cluster cluster name register ecs debug var ecs only service are listed while we have about services expected results get full list of services actual results ok ecs ansible facts services arn aws ecs us east service clustername import xxx arn aws ecs us east service clustername logistic aaa event arn aws ecs us east service clustername test mapping arn aws ecs us east service clustername consumer xxx arn aws ecs us east service clustername searcr arn aws ecs us east service clustername sales test aaa arn aws ecs us east service clustername sales test ggg arn aws ecs us east service clustername price test arn aws ecs us east service clustername shipment test arn aws ecs us east service clustername changed false | 1 |
4,003 | 18,675,840,547 | IssuesEvent | 2021-10-31 14:48:19 | RalfKoban/MiKo-Analyzers | https://api.github.com/repos/RalfKoban/MiKo-Analyzers | closed | Internal and private types should be either static or sealed | feature Area: analyzer Area: maintainability | Internal and private types should be either static or sealed unless derivation from them is required.
As with any implementation detail, they can be easily changed if/when derivation is required in the future. | True | Internal and private types should be either static or sealed - Internal and private types should be either static or sealed unless derivation from them is required.
As with any implementation detail, they can be easily changed if/when derivation is required in the future. | main | internal and private types should be either static or sealed internal and private types should be either static or sealed unless derivation from them is required as with any implementation detail they can be easily changed if when derivation is required in the future | 1 |
58,219 | 14,256,452,132 | IssuesEvent | 2020-11-20 01:02:34 | TIBCOSoftware/justapis-javascript-sdk | https://api.github.com/repos/TIBCOSoftware/justapis-javascript-sdk | closed | WS-2019-0019 (Medium) detected in braces-1.8.5.tgz - autoclosed | security vulnerability | ## WS-2019-0019 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>braces-1.8.5.tgz</b></p></summary>
<p>Fastest brace expansion for node.js, with the most complete support for the Bash 4.3 braces specification.</p>
<p>Library home page: <a href="https://registry.npmjs.org/braces/-/braces-1.8.5.tgz">https://registry.npmjs.org/braces/-/braces-1.8.5.tgz</a></p>
<p>Path to dependency file: /justapis-javascript-sdk/package.json</p>
<p>Path to vulnerable library: justapis-javascript-sdk/node_modules/braces/package.json</p>
<p>
Dependency Hierarchy:
- commitizen-2.10.1.tgz (Root Library)
- find-node-modules-1.0.4.tgz
- findup-sync-0.4.2.tgz
- micromatch-2.3.11.tgz
- :x: **braces-1.8.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/TIBCOSoftware/justapis-javascript-sdk/commits/3ca192403e92db3173fd513bbb67c49050b748e7">3ca192403e92db3173fd513bbb67c49050b748e7</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Version of braces prior to 2.3.1 are vulnerable to Regular Expression Denial of Service (ReDoS). Untrusted input may cause catastrophic backtracking while matching regular expressions. This can cause the application to be unresponsive leading to Denial of Service.
<p>Publish Date: 2018-02-16
<p>URL: <a href=https://github.com/micromatch/braces/commit/abdafb0cae1e0c00f184abbadc692f4eaa98f451>WS-2019-0019</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/786">https://www.npmjs.com/advisories/786</a></p>
<p>Release Date: 2019-02-21</p>
<p>Fix Resolution: 2.3.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"braces","packageVersion":"1.8.5","isTransitiveDependency":true,"dependencyTree":"commitizen:2.10.1;find-node-modules:1.0.4;findup-sync:0.4.2;micromatch:2.3.11;braces:1.8.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.3.1"}],"vulnerabilityIdentifier":"WS-2019-0019","vulnerabilityDetails":"Version of braces prior to 2.3.1 are vulnerable to Regular Expression Denial of Service (ReDoS). Untrusted input may cause catastrophic backtracking while matching regular expressions. This can cause the application to be unresponsive leading to Denial of Service.","vulnerabilityUrl":"https://github.com/micromatch/braces/commit/abdafb0cae1e0c00f184abbadc692f4eaa98f451","cvss2Severity":"medium","cvss2Score":"5.0","extraData":{}}</REMEDIATE> --> | True | WS-2019-0019 (Medium) detected in braces-1.8.5.tgz - autoclosed - ## WS-2019-0019 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>braces-1.8.5.tgz</b></p></summary>
<p>Fastest brace expansion for node.js, with the most complete support for the Bash 4.3 braces specification.</p>
<p>Library home page: <a href="https://registry.npmjs.org/braces/-/braces-1.8.5.tgz">https://registry.npmjs.org/braces/-/braces-1.8.5.tgz</a></p>
<p>Path to dependency file: /justapis-javascript-sdk/package.json</p>
<p>Path to vulnerable library: justapis-javascript-sdk/node_modules/braces/package.json</p>
<p>
Dependency Hierarchy:
- commitizen-2.10.1.tgz (Root Library)
- find-node-modules-1.0.4.tgz
- findup-sync-0.4.2.tgz
- micromatch-2.3.11.tgz
- :x: **braces-1.8.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/TIBCOSoftware/justapis-javascript-sdk/commits/3ca192403e92db3173fd513bbb67c49050b748e7">3ca192403e92db3173fd513bbb67c49050b748e7</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Version of braces prior to 2.3.1 are vulnerable to Regular Expression Denial of Service (ReDoS). Untrusted input may cause catastrophic backtracking while matching regular expressions. This can cause the application to be unresponsive leading to Denial of Service.
<p>Publish Date: 2018-02-16
<p>URL: <a href=https://github.com/micromatch/braces/commit/abdafb0cae1e0c00f184abbadc692f4eaa98f451>WS-2019-0019</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/786">https://www.npmjs.com/advisories/786</a></p>
<p>Release Date: 2019-02-21</p>
<p>Fix Resolution: 2.3.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"braces","packageVersion":"1.8.5","isTransitiveDependency":true,"dependencyTree":"commitizen:2.10.1;find-node-modules:1.0.4;findup-sync:0.4.2;micromatch:2.3.11;braces:1.8.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.3.1"}],"vulnerabilityIdentifier":"WS-2019-0019","vulnerabilityDetails":"Version of braces prior to 2.3.1 are vulnerable to Regular Expression Denial of Service (ReDoS). Untrusted input may cause catastrophic backtracking while matching regular expressions. This can cause the application to be unresponsive leading to Denial of Service.","vulnerabilityUrl":"https://github.com/micromatch/braces/commit/abdafb0cae1e0c00f184abbadc692f4eaa98f451","cvss2Severity":"medium","cvss2Score":"5.0","extraData":{}}</REMEDIATE> --> | non_main | ws medium detected in braces tgz autoclosed ws medium severity vulnerability vulnerable library braces tgz fastest brace expansion for node js with the most complete support for the bash braces specification library home page a href path to dependency file justapis javascript sdk package json path to vulnerable library justapis javascript sdk node modules braces package json dependency hierarchy commitizen tgz root library find node modules tgz findup sync tgz micromatch tgz x braces tgz vulnerable library found in head commit a href vulnerability details version of braces prior to are vulnerable to regular expression denial of service redos untrusted input may cause catastrophic backtracking while matching regular expressions this can cause the application to be unresponsive leading to denial of service publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier ws vulnerabilitydetails version of braces prior to are vulnerable to regular expression denial of service redos untrusted input may cause catastrophic backtracking while matching regular expressions this can cause the application to be unresponsive leading to denial of service vulnerabilityurl | 0 |
5,859 | 31,475,641,063 | IssuesEvent | 2023-08-30 10:29:04 | pypiserver/pypiserver | https://api.github.com/repos/pypiserver/pypiserver | closed | Docker is (no longer 🎉) moving to paid organisations (but still 💭) | type.Maintainance status.STICKY tag.docker | See https://blog.alexellis.io/docker-is-deleting-open-source-images/
and https://news.ycombinator.com/item?id=35166317
We use an organization account for pypiserver, so we’ll need to move. GitHub container registry seems like a reasonable choice.
We could probably qualify for docker’s open source program, but it seems like applications are taking over a year to process at the moment. | True | Docker is (no longer 🎉) moving to paid organisations (but still 💭) - See https://blog.alexellis.io/docker-is-deleting-open-source-images/
and https://news.ycombinator.com/item?id=35166317
We use an organization account for pypiserver, so we’ll need to move. GitHub container registry seems like a reasonable choice.
We could probably qualify for docker’s open source program, but it seems like applications are taking over a year to process at the moment. | main | docker is no longer 🎉 moving to paid organisations but still 💭 see and we use an organization account for pypiserver so we’ll need to move github container registry seems like a reasonable choice we could probably qualify for docker’s open source program but it seems like applications are taking over a year to process at the moment | 1 |
1,368 | 5,920,854,141 | IssuesEvent | 2017-05-22 21:19:36 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | unarchive: Cannot unpack from URL under Python 3 | affects_2.2 bug_report python3 waiting_on_maintainer | ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
- files/unarchive
##### ANSIBLE VERSION
```
ansible 2.2.0.0 (detached HEAD cdec853e37) last updated 2016/12/01 10:23:30 (GMT +200)
lib/ansible/modules/core: (detached HEAD fe9c56a003) last updated 2016/12/01 10:24:42 (GMT +200)
lib/ansible/modules/extras: (detached HEAD f564e77a08) last updated 2016/12/01 10:24:42 (GMT +200)
config file =
configured module search path = ['/Users/per/Projects/servers/submodules/ansible/library']
```
##### CONFIGURATION
- ansible_python_interpreter=/usr/bin/python3
##### OS / ENVIRONMENT
- Local: MacOS
- Remote: Ubuntu 16.04, with Python 3
##### SUMMARY
Unarchive breaks when downloading from HTTP. Probably caused by running Ansible under Python 3 remotely (but not locally).
##### STEPS TO REPRODUCE
```
bin/ansible *** -m unarchive \
-a "src=http://downloads.rclone.org/rclone-v1.34-linux-amd64.zip \
remote_src=yes \
dest=/opt \
creates=/opt/rclone-v1.34-linux-amd64"
```
##### EXPECTED RESULTS
- Download and unpacking (if needed)
##### ACTUAL RESULTS
```
*** | FAILED! => {
"changed": false,
"failed": true,
"msg": "Failure downloading http://downloads.rclone.org/rclone-v1.34-linux-amd64.zip, write() argument must be str, not bytes"
}
```
| True | unarchive: Cannot unpack from URL under Python 3 - ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
- files/unarchive
##### ANSIBLE VERSION
```
ansible 2.2.0.0 (detached HEAD cdec853e37) last updated 2016/12/01 10:23:30 (GMT +200)
lib/ansible/modules/core: (detached HEAD fe9c56a003) last updated 2016/12/01 10:24:42 (GMT +200)
lib/ansible/modules/extras: (detached HEAD f564e77a08) last updated 2016/12/01 10:24:42 (GMT +200)
config file =
configured module search path = ['/Users/per/Projects/servers/submodules/ansible/library']
```
##### CONFIGURATION
- ansible_python_interpreter=/usr/bin/python3
##### OS / ENVIRONMENT
- Local: MacOS
- Remote: Ubuntu 16.04, with Python 3
##### SUMMARY
Unarchive breaks when downloading from HTTP. Probably caused by running Ansible under Python 3 remotely (but not locally).
##### STEPS TO REPRODUCE
```
bin/ansible *** -m unarchive \
-a "src=http://downloads.rclone.org/rclone-v1.34-linux-amd64.zip \
remote_src=yes \
dest=/opt \
creates=/opt/rclone-v1.34-linux-amd64"
```
##### EXPECTED RESULTS
- Download and unpacking (if needed)
##### ACTUAL RESULTS
```
*** | FAILED! => {
"changed": false,
"failed": true,
"msg": "Failure downloading http://downloads.rclone.org/rclone-v1.34-linux-amd64.zip, write() argument must be str, not bytes"
}
```
| main | unarchive cannot unpack from url under python issue type bug report component name files unarchive ansible version ansible detached head last updated gmt lib ansible modules core detached head last updated gmt lib ansible modules extras detached head last updated gmt config file configured module search path configuration ansible python interpreter usr bin os environment local macos remote ubuntu with python summary unarchive breaks when downloading from http probably caused by running ansible under python remotely but not locally steps to reproduce bin ansible m unarchive a src remote src yes dest opt creates opt rclone linux expected results download and unpacking if needed actual results failed changed false failed true msg failure downloading write argument must be str not bytes | 1 |
3,955 | 17,946,986,162 | IssuesEvent | 2021-09-12 01:22:42 | restqa/restqa | https://api.github.com/repos/restqa/restqa | closed | [DASHBOARD] Track source of traffic for the sponsors | enhancement good first issue help wanted pair with maintainer | Hello 👋,
### 👀 Background
Sponsors have their logo displayed on the dashboard, however there is no way for the sponsor to know that someone access to their website from the RestQA dashboard
### ✌️ What is the actual behavior?
On the RestQA Dashboard main page when the user is clicking on the logo he is redirected to the sponsor website.
### 🕵️♀️ How to reproduce the current behavior?
* Clone the repository
* Install the dependencies : `npm i`
* Install the dependencies of the dashboard: `npm run dashboard:install`
* Run the dashboard on dev mode: `npm run dashboard:dev`
* Access to the dashboard from your browser http://localhost:8081
* Click on one for the sponsor logo.
### 🤞 What is the expected behavior?
When we click on the sponsor logo we should be redirected to the sponsor website, the sponsor should be able to know the source of the traffic
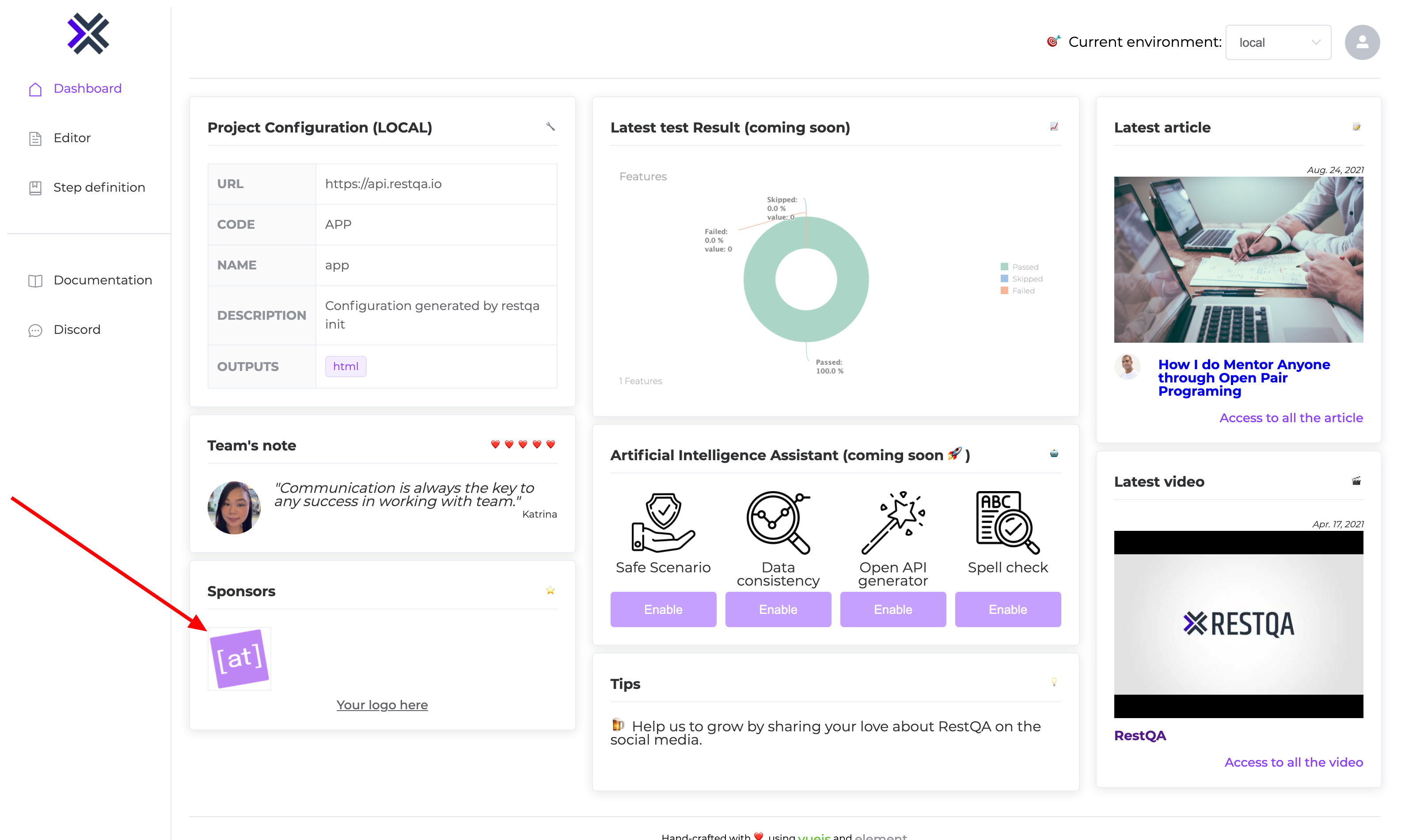
### 😎 Proposed solution.
- [ ] Add utm information on the sponsor url: `https://example.com?utm_source=dashboard&utm_medium=referral&utm_campaign=restqa`
Cheers.
| True | [DASHBOARD] Track source of traffic for the sponsors - Hello 👋,
### 👀 Background
Sponsors have their logo displayed on the dashboard, however there is no way for the sponsor to know that someone access to their website from the RestQA dashboard
### ✌️ What is the actual behavior?
On the RestQA Dashboard main page when the user is clicking on the logo he is redirected to the sponsor website.
### 🕵️♀️ How to reproduce the current behavior?
* Clone the repository
* Install the dependencies : `npm i`
* Install the dependencies of the dashboard: `npm run dashboard:install`
* Run the dashboard on dev mode: `npm run dashboard:dev`
* Access to the dashboard from your browser http://localhost:8081
* Click on one for the sponsor logo.
### 🤞 What is the expected behavior?
When we click on the sponsor logo we should be redirected to the sponsor website, the sponsor should be able to know the source of the traffic
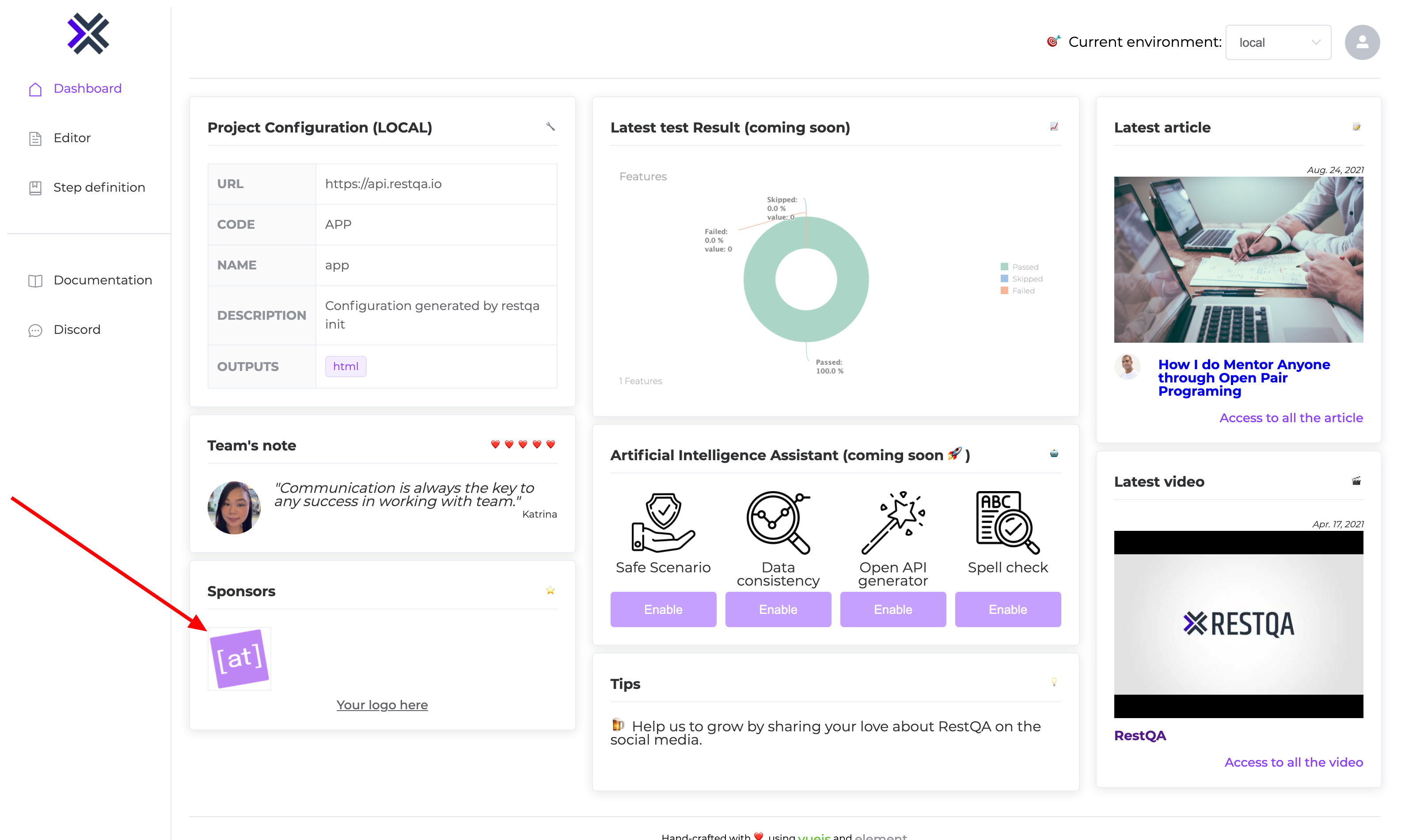
### 😎 Proposed solution.
- [ ] Add utm information on the sponsor url: `https://example.com?utm_source=dashboard&utm_medium=referral&utm_campaign=restqa`
Cheers.
| main | track source of traffic for the sponsors hello 👋 👀 background sponsors have their logo displayed on the dashboard however there is no way for the sponsor to know that someone access to their website from the restqa dashboard ✌️ what is the actual behavior on the restqa dashboard main page when the user is clicking on the logo he is redirected to the sponsor website 🕵️♀️ how to reproduce the current behavior clone the repository install the dependencies npm i install the dependencies of the dashboard npm run dashboard install run the dashboard on dev mode npm run dashboard dev access to the dashboard from your browser click on one for the sponsor logo 🤞 what is the expected behavior when we click on the sponsor logo we should be redirected to the sponsor website the sponsor should be able to know the source of the traffic 😎 proposed solution add utm information on the sponsor url cheers | 1 |
117,491 | 11,948,389,177 | IssuesEvent | 2020-04-03 11:46:05 | Financial-Times/origami-website | https://api.github.com/repos/Financial-Times/origami-website | closed | Remove OBT from the manual build demo | documentation website | We intend to replace Origami Build Tools (OBT) with Origami Authoring Tools (OAT), which will focus on authoring components and not building projects. We should remove OBT from the manual build tutorial, probably replacing it with a [Parcel demo](https://github.com/JakeChampion/parcel-origami-example). | 1.0 | Remove OBT from the manual build demo - We intend to replace Origami Build Tools (OBT) with Origami Authoring Tools (OAT), which will focus on authoring components and not building projects. We should remove OBT from the manual build tutorial, probably replacing it with a [Parcel demo](https://github.com/JakeChampion/parcel-origami-example). | non_main | remove obt from the manual build demo we intend to replace origami build tools obt with origami authoring tools oat which will focus on authoring components and not building projects we should remove obt from the manual build tutorial probably replacing it with a | 0 |
1,326 | 5,694,126,370 | IssuesEvent | 2017-04-15 09:45:29 | beefproject/beef | https://api.github.com/repos/beefproject/beef | closed | Store loot in home directory | Maintainability | A few modules write data to the BeEF root directory.
They should be updated to write to a `data` directory in the BeEF folder, or `~/.beef/`
- modules/host/get_wireless_keys/
- modules/browser/spyder_eye/
The output filename should be modified to reflect the timestamp, hooked browser id or IP address, module name and possible the command ID.
Also, these modules don't save a PNG to disk, but probably should:
- modules/browser/webcam/
- modules/browser/webcam_html5/
Also, some modules retrieve information, such as credentials. These should also be saved to disk.
| True | Store loot in home directory - A few modules write data to the BeEF root directory.
They should be updated to write to a `data` directory in the BeEF folder, or `~/.beef/`
- modules/host/get_wireless_keys/
- modules/browser/spyder_eye/
The output filename should be modified to reflect the timestamp, hooked browser id or IP address, module name and possible the command ID.
Also, these modules don't save a PNG to disk, but probably should:
- modules/browser/webcam/
- modules/browser/webcam_html5/
Also, some modules retrieve information, such as credentials. These should also be saved to disk.
| main | store loot in home directory a few modules write data to the beef root directory they should be updated to write to a data directory in the beef folder or beef modules host get wireless keys modules browser spyder eye the output filename should be modified to reflect the timestamp hooked browser id or ip address module name and possible the command id also these modules don t save a png to disk but probably should modules browser webcam modules browser webcam also some modules retrieve information such as credentials these should also be saved to disk | 1 |
4,431 | 23,038,089,752 | IssuesEvent | 2022-07-22 21:34:16 | Lissy93/dashy | https://api.github.com/repos/Lissy93/dashy | closed | [BUG] TypeError: Cannot read properties of undefined (reading 'push') | 🐛 Bug 👤 Awaiting Maintainer Response | ### Environment
Self-Hosted (Docker)
### System
Ubuntu 22.04 running on arm64
### Version
2.1.1
### Describe the problem
First of all - thank you for your project! I can finally organize my home environment and stop having to remember 40 random ports :D
I've installed Dashy 2.1.1 via the docker-compose method. I mapped the configuration file to /etc/dashy.yml on my host (and gave it enough permissions to be writable). The docker instance started correctly. When I enter Config -> Enter the interactive editor and click on the "Add new section" in the GUI, I get the "Add new section" popup as expected. I filled in "Section Name" with "Home Automation" and left the other options blank. I clicked Save and nothing happened visually. I opened the developer console and I got the following traceback (repeated every time I clicked "Save"):
```
TypeError: Cannot read properties of undefined (reading 'push')
at f.<anonymous> (dashy.9f0ff4c4.js:1:427855)
at vuex.esm.js:844:13
at vuex.esm.js:466:7
at Array.forEach (<anonymous>)
at vuex.esm.js:465:11
at f._withCommit (vuex.esm.js:624:3)
at f.commit (vuex.esm.js:464:8)
at f.commit (vuex.esm.js:409:19)
at r.saveSection (EditPageInfo.vue?a59e:100:1)
at click (interactive-editor-add.svg:1:384)
```
I've tested with Firefox 95.0b4 and Chromium 103.0.5060.114 and it happens on both.
Funny thing - now that I'm submitting this and redoing my steps - it started to work... :confused: I haven't made any changes...
Well, hope this helps identify the issue (if any).
Thanks again!
### Additional info
_No response_
### Please tick the boxes
- [X] You have explained the issue clearly, and included all relevant info
- [X] You are using a [supported](https://github.com/Lissy93/dashy/blob/master/.github/SECURITY.md#supported-versions) version of Dashy
- [X] You've checked that this [issue hasn't already been raised](https://github.com/Lissy93/dashy/issues?q=is%3Aissue)
- [X] You've checked the [docs](https://github.com/Lissy93/dashy/tree/master/docs#readme) and [troubleshooting](https://github.com/Lissy93/dashy/blob/master/docs/troubleshooting.md#troubleshooting) guide 
- [X] You agree to the [code of conduct](https://github.com/Lissy93/dashy/blob/master/.github/CODE_OF_CONDUCT.md#contributor-covenant-code-of-conduct) | True | [BUG] TypeError: Cannot read properties of undefined (reading 'push') - ### Environment
Self-Hosted (Docker)
### System
Ubuntu 22.04 running on arm64
### Version
2.1.1
### Describe the problem
First of all - thank you for your project! I can finally organize my home environment and stop having to remember 40 random ports :D
I've installed Dashy 2.1.1 via the docker-compose method. I mapped the configuration file to /etc/dashy.yml on my host (and gave it enough permissions to be writable). The docker instance started correctly. When I enter Config -> Enter the interactive editor and click on the "Add new section" in the GUI, I get the "Add new section" popup as expected. I filled in "Section Name" with "Home Automation" and left the other options blank. I clicked Save and nothing happened visually. I opened the developer console and I got the following traceback (repeated every time I clicked "Save"):
```
TypeError: Cannot read properties of undefined (reading 'push')
at f.<anonymous> (dashy.9f0ff4c4.js:1:427855)
at vuex.esm.js:844:13
at vuex.esm.js:466:7
at Array.forEach (<anonymous>)
at vuex.esm.js:465:11
at f._withCommit (vuex.esm.js:624:3)
at f.commit (vuex.esm.js:464:8)
at f.commit (vuex.esm.js:409:19)
at r.saveSection (EditPageInfo.vue?a59e:100:1)
at click (interactive-editor-add.svg:1:384)
```
I've tested with Firefox 95.0b4 and Chromium 103.0.5060.114 and it happens on both.
Funny thing - now that I'm submitting this and redoing my steps - it started to work... :confused: I haven't made any changes...
Well, hope this helps identify the issue (if any).
Thanks again!
### Additional info
_No response_
### Please tick the boxes
- [X] You have explained the issue clearly, and included all relevant info
- [X] You are using a [supported](https://github.com/Lissy93/dashy/blob/master/.github/SECURITY.md#supported-versions) version of Dashy
- [X] You've checked that this [issue hasn't already been raised](https://github.com/Lissy93/dashy/issues?q=is%3Aissue)
- [X] You've checked the [docs](https://github.com/Lissy93/dashy/tree/master/docs#readme) and [troubleshooting](https://github.com/Lissy93/dashy/blob/master/docs/troubleshooting.md#troubleshooting) guide 
- [X] You agree to the [code of conduct](https://github.com/Lissy93/dashy/blob/master/.github/CODE_OF_CONDUCT.md#contributor-covenant-code-of-conduct) | main | typeerror cannot read properties of undefined reading push environment self hosted docker system ubuntu running on version describe the problem first of all thank you for your project i can finally organize my home environment and stop having to remember random ports d i ve installed dashy via the docker compose method i mapped the configuration file to etc dashy yml on my host and gave it enough permissions to be writable the docker instance started correctly when i enter config enter the interactive editor and click on the add new section in the gui i get the add new section popup as expected i filled in section name with home automation and left the other options blank i clicked save and nothing happened visually i opened the developer console and i got the following traceback repeated every time i clicked save typeerror cannot read properties of undefined reading push at f dashy js at vuex esm js at vuex esm js at array foreach at vuex esm js at f withcommit vuex esm js at f commit vuex esm js at f commit vuex esm js at r savesection editpageinfo vue at click interactive editor add svg i ve tested with firefox and chromium and it happens on both funny thing now that i m submitting this and redoing my steps it started to work confused i haven t made any changes well hope this helps identify the issue if any thanks again additional info no response please tick the boxes you have explained the issue clearly and included all relevant info you are using a version of dashy you ve checked that this you ve checked the and guide you agree to the | 1 |
3,151 | 12,155,911,611 | IssuesEvent | 2020-04-25 15:09:35 | diofant/diofant | https://api.github.com/repos/diofant/diofant | closed | Port sqfreetools module to use sparse polys | enhancement maintainability polys | This include implementing is_squarefree, sqf_norm, sqf_part and sqf_list methods for PolyElement. See [TODO](https://github.com/diofant/diofant/blob/987094a0a22b101e545e291af5ee9f526233f279/diofant/polys/rings.py#L2058-L2059). | True | Port sqfreetools module to use sparse polys - This include implementing is_squarefree, sqf_norm, sqf_part and sqf_list methods for PolyElement. See [TODO](https://github.com/diofant/diofant/blob/987094a0a22b101e545e291af5ee9f526233f279/diofant/polys/rings.py#L2058-L2059). | main | port sqfreetools module to use sparse polys this include implementing is squarefree sqf norm sqf part and sqf list methods for polyelement see | 1 |
264,801 | 23,139,650,500 | IssuesEvent | 2022-07-28 17:10:34 | o3de/o3de | https://api.github.com/repos/o3de/o3de | opened | Test Tools: launcher_platform parameterization behaves unexpectedly | kind/bug needs-triage sig/testing | **Describe the bug**
launcher_platform parameterization behaves unexpectedly. Test suites that only have `@pytest.mark.parametrize("launcher_platform", ['windows_editor'])` specified will still run on Linux. To skip tests on Linux, users must use a `@pytest.mark.skipif' statement or alternatively setup PAL traits flags for their tests, e.g.
AutomatedTesting/Gem/PythonTests/Platform/Linux/PAL_traits_linux.cmake
```
#
# Copyright (c) Contributors to the Open 3D Engine Project.
# For complete copyright and license terms please see the LICENSE at the root of this distribution.
#
# SPDX-License-Identifier: Apache-2.0 OR MIT
#
#
set(PAL_TRAIT_LARGE_WORLDS_TEST_SUPPORTED FALSE)
```
**Steps to reproduce**
1. Run any test suite with only windows_editor parametrized on Linux.
**Expected behavior**
Tests will not run.
**Actual behavior**
Tests run, unless user has explicitly skipif'd or setup platform PAL traits.
**Found in Branch**
development@ 3cd9628b764fed1ab715bb65ee4b1cb7005d4512
**Additional Info**
1. The same appears to be true for Game Launcher tests utilizing the @pytest.mark.parametrize("launcher_platform", ['windows'])` parameterization. Tests will still attempt to run on Linux, but currently will hit an error in create_game_launcher:
```
[2022-07-28T00:08:21.790Z] ==================================== ERRORS ====================================
[2022-07-28T00:08:21.790Z] _ ERROR at setup of TestLauncherAutomation.test_Launcher_MultipleLevelLoads[linux-AutomatedTesting-windows] _
[2022-07-28T00:08:21.790Z] ../../../../../../Tools/LyTestTools/ly_test_tools/_internal/pytest_plugin/test_tools_fixtures.py:237: in launcher
[2022-07-28T00:08:21.790Z] level=get_fixture_argument(request, 'level', ''))
[2022-07-28T00:08:21.790Z] ../../../../../../Tools/LyTestTools/ly_test_tools/_internal/pytest_plugin/test_tools_fixtures.py:245: in _launcher
[2022-07-28T00:08:21.790Z] workspace, launcher_platform)
[2022-07-28T00:08:21.790Z] ../../../../../../Tools/LyTestTools/ly_test_tools/launchers/launcher_helper.py:62: in create_game_launcher
[2022-07-28T00:08:21.790Z] return launcher_class(workspace, args)
[2022-07-28T00:08:21.790Z] E TypeError: 'NoneType' object is not callable
[2022-07-28T00:08:21.790Z] ---------------------------- Captured stdout setup -----------------------------
``` | 1.0 | Test Tools: launcher_platform parameterization behaves unexpectedly - **Describe the bug**
launcher_platform parameterization behaves unexpectedly. Test suites that only have `@pytest.mark.parametrize("launcher_platform", ['windows_editor'])` specified will still run on Linux. To skip tests on Linux, users must use a `@pytest.mark.skipif' statement or alternatively setup PAL traits flags for their tests, e.g.
AutomatedTesting/Gem/PythonTests/Platform/Linux/PAL_traits_linux.cmake
```
#
# Copyright (c) Contributors to the Open 3D Engine Project.
# For complete copyright and license terms please see the LICENSE at the root of this distribution.
#
# SPDX-License-Identifier: Apache-2.0 OR MIT
#
#
set(PAL_TRAIT_LARGE_WORLDS_TEST_SUPPORTED FALSE)
```
**Steps to reproduce**
1. Run any test suite with only windows_editor parametrized on Linux.
**Expected behavior**
Tests will not run.
**Actual behavior**
Tests run, unless user has explicitly skipif'd or setup platform PAL traits.
**Found in Branch**
development@ 3cd9628b764fed1ab715bb65ee4b1cb7005d4512
**Additional Info**
1. The same appears to be true for Game Launcher tests utilizing the @pytest.mark.parametrize("launcher_platform", ['windows'])` parameterization. Tests will still attempt to run on Linux, but currently will hit an error in create_game_launcher:
```
[2022-07-28T00:08:21.790Z] ==================================== ERRORS ====================================
[2022-07-28T00:08:21.790Z] _ ERROR at setup of TestLauncherAutomation.test_Launcher_MultipleLevelLoads[linux-AutomatedTesting-windows] _
[2022-07-28T00:08:21.790Z] ../../../../../../Tools/LyTestTools/ly_test_tools/_internal/pytest_plugin/test_tools_fixtures.py:237: in launcher
[2022-07-28T00:08:21.790Z] level=get_fixture_argument(request, 'level', ''))
[2022-07-28T00:08:21.790Z] ../../../../../../Tools/LyTestTools/ly_test_tools/_internal/pytest_plugin/test_tools_fixtures.py:245: in _launcher
[2022-07-28T00:08:21.790Z] workspace, launcher_platform)
[2022-07-28T00:08:21.790Z] ../../../../../../Tools/LyTestTools/ly_test_tools/launchers/launcher_helper.py:62: in create_game_launcher
[2022-07-28T00:08:21.790Z] return launcher_class(workspace, args)
[2022-07-28T00:08:21.790Z] E TypeError: 'NoneType' object is not callable
[2022-07-28T00:08:21.790Z] ---------------------------- Captured stdout setup -----------------------------
``` | non_main | test tools launcher platform parameterization behaves unexpectedly describe the bug launcher platform parameterization behaves unexpectedly test suites that only have pytest mark parametrize launcher platform specified will still run on linux to skip tests on linux users must use a pytest mark skipif statement or alternatively setup pal traits flags for their tests e g automatedtesting gem pythontests platform linux pal traits linux cmake copyright c contributors to the open engine project for complete copyright and license terms please see the license at the root of this distribution spdx license identifier apache or mit set pal trait large worlds test supported false steps to reproduce run any test suite with only windows editor parametrized on linux expected behavior tests will not run actual behavior tests run unless user has explicitly skipif d or setup platform pal traits found in branch development additional info the same appears to be true for game launcher tests utilizing the pytest mark parametrize launcher platform parameterization tests will still attempt to run on linux but currently will hit an error in create game launcher errors error at setup of testlauncherautomation test launcher multiplelevelloads tools lytesttools ly test tools internal pytest plugin test tools fixtures py in launcher level get fixture argument request level tools lytesttools ly test tools internal pytest plugin test tools fixtures py in launcher workspace launcher platform tools lytesttools ly test tools launchers launcher helper py in create game launcher return launcher class workspace args e typeerror nonetype object is not callable captured stdout setup | 0 |
63,938 | 14,656,808,626 | IssuesEvent | 2020-12-28 14:14:45 | fu1771695yongxie/yapi | https://api.github.com/repos/fu1771695yongxie/yapi | opened | CVE-2018-16492 (High) detected in extend-3.0.1.tgz | security vulnerability | ## CVE-2018-16492 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>extend-3.0.1.tgz</b></p></summary>
<p>Port of jQuery.extend for node.js and the browser</p>
<p>Library home page: <a href="https://registry.npmjs.org/extend/-/extend-3.0.1.tgz">https://registry.npmjs.org/extend/-/extend-3.0.1.tgz</a></p>
<p>Path to dependency file: yapi/package.json</p>
<p>Path to vulnerable library: yapi/node_modules/extend/package.json</p>
<p>
Dependency Hierarchy:
- mongoose-auto-increment-5.0.1.tgz (Root Library)
- :x: **extend-3.0.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/fu1771695yongxie/yapi/commit/426884f4927afe9500db9cacc24729657b10526b">426884f4927afe9500db9cacc24729657b10526b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A prototype pollution vulnerability was found in module extend <2.0.2, ~<3.0.2 that allows an attacker to inject arbitrary properties onto Object.prototype.
<p>Publish Date: 2019-02-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16492>CVE-2018-16492</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://hackerone.com/reports/381185">https://hackerone.com/reports/381185</a></p>
<p>Release Date: 2019-02-01</p>
<p>Fix Resolution: extend - v3.0.2,v2.0.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-16492 (High) detected in extend-3.0.1.tgz - ## CVE-2018-16492 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>extend-3.0.1.tgz</b></p></summary>
<p>Port of jQuery.extend for node.js and the browser</p>
<p>Library home page: <a href="https://registry.npmjs.org/extend/-/extend-3.0.1.tgz">https://registry.npmjs.org/extend/-/extend-3.0.1.tgz</a></p>
<p>Path to dependency file: yapi/package.json</p>
<p>Path to vulnerable library: yapi/node_modules/extend/package.json</p>
<p>
Dependency Hierarchy:
- mongoose-auto-increment-5.0.1.tgz (Root Library)
- :x: **extend-3.0.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/fu1771695yongxie/yapi/commit/426884f4927afe9500db9cacc24729657b10526b">426884f4927afe9500db9cacc24729657b10526b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A prototype pollution vulnerability was found in module extend <2.0.2, ~<3.0.2 that allows an attacker to inject arbitrary properties onto Object.prototype.
<p>Publish Date: 2019-02-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16492>CVE-2018-16492</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://hackerone.com/reports/381185">https://hackerone.com/reports/381185</a></p>
<p>Release Date: 2019-02-01</p>
<p>Fix Resolution: extend - v3.0.2,v2.0.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_main | cve high detected in extend tgz cve high severity vulnerability vulnerable library extend tgz port of jquery extend for node js and the browser library home page a href path to dependency file yapi package json path to vulnerable library yapi node modules extend package json dependency hierarchy mongoose auto increment tgz root library x extend tgz vulnerable library found in head commit a href found in base branch master vulnerability details a prototype pollution vulnerability was found in module extend that allows an attacker to inject arbitrary properties onto object prototype publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution extend step up your open source security game with whitesource | 0 |
359,446 | 25,237,370,835 | IssuesEvent | 2022-11-15 02:50:03 | BlazorComponent/MASA.Blazor | https://api.github.com/repos/BlazorComponent/MASA.Blazor | opened | MASA Blazor New document task list | type/documentation | ### MASA Blazor新文档功能清单
以下是剩余的任务列表,这将每天更新,所以要注意变化。
The following is the list of remaining tasks, which will be updated daily, so pay attention to changes..
### 待办事项列表 (To Do List)
<hr />
- [x] 文档框架核心 (Document framework core)
- [ ] 左侧导航 (Left Navigation)
- [ ] 导航内容 (Navigation content)
- [ ] 介绍 (Introduction)
- [ ] 快速入门 (Getting started)
- [ ] 特性 (Features)
- [ ] 样式和动画 (Styles and animations)
- [ ] 关于 (About)
- [ ] 功能和样式 (Function and style)
- [ ] 版本切换 (Version switching)
- [ ] 样式还原 (Style Restore)
- [ ] 和顶部导航联动 (Linkage with top navigation)
- [ ] 国际化 (I18N)
- [ ] 导航标签 (Navigation label)
- [ ] 顶部导航 (Top Navigation)
- [ ] 导航内容 (Navigation content)
- [ ] 文档中心 (Document center)
- [ ] 新手入门 (Getting started)
- [ ] Pro
- [ ] 博客 (Blog)
- [ ] 社区 (Community)
- [ ] 官网 (Official website)
- [ ] 开源地址链接 ()
- [ ] 功能和样式 (Function and style)
- [ ] 样式还原 (Style Restore)
- [ ] 和左侧导航联动 ()
- [ ] 导航标签 (Navigation label)
- [ ] 全文检索(Algolia) (Full text retrieval (Algolia))
- [ ] 语言切换 (Language switching)
- [ ] 设置 (Settings)
- [ ] 右侧导航 (Right Navigation)
- [ ] 对接Github(issues)数据 (Docking Github (issues) data)
- [ ] 目录标签 (Catalog Label)
- [ ] 赞助商 (Sponsor)
- [ ] 样式还原 (Style Restore)
### UI组件
当满足以下条件时,组件文档被视为已完成:
- 每个组件API文档中的每个属性、事件、插槽等都有相应的描述并且API文档支持I18n切换。
The component document is considered completed when the following conditions are met:
- Each attribute, event, slot, etc. in each component API document has a corresponding description, and the API document supports I18n switching.
- [ ] alerts
- [ ] application
- [ ] aspect-ratios
- [ ] avatars
- [ ] badges
- [ ] banners
- [ ] bars
- [ ] app-bars
- [ ] toolbars
- [ ] system-bars
- [ ] block-text
- [ ] borders
- [ ] bottom-navigation
- [ ] bottom-sheets
- [ ] breadcrumbs
- [ ] buttons
- [ ] cards
- [ ] carousels
- [ ] chips
- [ ] copyable-text
- [ ] cron
- [ ] dialogs
- [ ] dividers
- [ ] drag-zone
- [ ] drawers
- [ ] echarts
- [ ] editor
- [ ] error-handler
- [ ] expansion-panels
- [ ] floating-action-buttons
- [ ] footers
- [ ] form-inputs-and-ontrols
- [ ] autocomplete
- [ ] cascaders
- [ ] checkboxes
- [ ] file-inputs
- [ ] forms
- [ ] otp-input
- [ ] radio
- [ ] range-sliders
- [ ] selects
- [ ] sliders
- [ ] switches
- [ ] textareas
- [ ] text-fields
- [ ] grids
- [ ] groups
- [ ] button-groups
- [ ] chip-groups
- [ ] item-groups
- [ ] list-item-groups
- [ ] slide-groups
- [ ] windows
- [ ] hover
- [ ] icons
- [ ] image-captcha
- [ ] images
- [ ] infinite-scroll
- [ ] lists
- [ ] markdown
- [ ] menus
- [ ] mobiles
- [ ] mobile-cascader
- [ ] mobile-date-pickers
- [ ] mobile-date-time-pickers
- [ ] mobile-pickers
- [ ] mobil-picker-views
- [ ] mobile-time-pickers
- [ ] modals
- [ ] navigation-drawers
- [ ] not-grouped
- [ ] overlays
- [ ] pagination
- [ ] Pickers
- [ ] date-pickers
- [ ] date-pickers-month
- [ ] time-pickers
- [ ] popup-service
- [ ] progress
- [ ] progress-circular
- [ ] progress-linear
- [ ] ratings
- [ ] sheets
- [ ] skeleton-loaders
- [ ] snackbars
- [ ] steppers
- [ ] subheaders
- [ ] tables
- [ ] data-iterators
- [ ] data-tables
- [ ] simple-tables
- [ ] tabs
- [ ] timelines
- [ ] toast
- [ ] tooltips
- [ ] treeview
- [ ] virtual-scroll
| 1.0 | MASA Blazor New document task list - ### MASA Blazor新文档功能清单
以下是剩余的任务列表,这将每天更新,所以要注意变化。
The following is the list of remaining tasks, which will be updated daily, so pay attention to changes..
### 待办事项列表 (To Do List)
<hr />
- [x] 文档框架核心 (Document framework core)
- [ ] 左侧导航 (Left Navigation)
- [ ] 导航内容 (Navigation content)
- [ ] 介绍 (Introduction)
- [ ] 快速入门 (Getting started)
- [ ] 特性 (Features)
- [ ] 样式和动画 (Styles and animations)
- [ ] 关于 (About)
- [ ] 功能和样式 (Function and style)
- [ ] 版本切换 (Version switching)
- [ ] 样式还原 (Style Restore)
- [ ] 和顶部导航联动 (Linkage with top navigation)
- [ ] 国际化 (I18N)
- [ ] 导航标签 (Navigation label)
- [ ] 顶部导航 (Top Navigation)
- [ ] 导航内容 (Navigation content)
- [ ] 文档中心 (Document center)
- [ ] 新手入门 (Getting started)
- [ ] Pro
- [ ] 博客 (Blog)
- [ ] 社区 (Community)
- [ ] 官网 (Official website)
- [ ] 开源地址链接 ()
- [ ] 功能和样式 (Function and style)
- [ ] 样式还原 (Style Restore)
- [ ] 和左侧导航联动 ()
- [ ] 导航标签 (Navigation label)
- [ ] 全文检索(Algolia) (Full text retrieval (Algolia))
- [ ] 语言切换 (Language switching)
- [ ] 设置 (Settings)
- [ ] 右侧导航 (Right Navigation)
- [ ] 对接Github(issues)数据 (Docking Github (issues) data)
- [ ] 目录标签 (Catalog Label)
- [ ] 赞助商 (Sponsor)
- [ ] 样式还原 (Style Restore)
### UI组件
当满足以下条件时,组件文档被视为已完成:
- 每个组件API文档中的每个属性、事件、插槽等都有相应的描述并且API文档支持I18n切换。
The component document is considered completed when the following conditions are met:
- Each attribute, event, slot, etc. in each component API document has a corresponding description, and the API document supports I18n switching.
- [ ] alerts
- [ ] application
- [ ] aspect-ratios
- [ ] avatars
- [ ] badges
- [ ] banners
- [ ] bars
- [ ] app-bars
- [ ] toolbars
- [ ] system-bars
- [ ] block-text
- [ ] borders
- [ ] bottom-navigation
- [ ] bottom-sheets
- [ ] breadcrumbs
- [ ] buttons
- [ ] cards
- [ ] carousels
- [ ] chips
- [ ] copyable-text
- [ ] cron
- [ ] dialogs
- [ ] dividers
- [ ] drag-zone
- [ ] drawers
- [ ] echarts
- [ ] editor
- [ ] error-handler
- [ ] expansion-panels
- [ ] floating-action-buttons
- [ ] footers
- [ ] form-inputs-and-ontrols
- [ ] autocomplete
- [ ] cascaders
- [ ] checkboxes
- [ ] file-inputs
- [ ] forms
- [ ] otp-input
- [ ] radio
- [ ] range-sliders
- [ ] selects
- [ ] sliders
- [ ] switches
- [ ] textareas
- [ ] text-fields
- [ ] grids
- [ ] groups
- [ ] button-groups
- [ ] chip-groups
- [ ] item-groups
- [ ] list-item-groups
- [ ] slide-groups
- [ ] windows
- [ ] hover
- [ ] icons
- [ ] image-captcha
- [ ] images
- [ ] infinite-scroll
- [ ] lists
- [ ] markdown
- [ ] menus
- [ ] mobiles
- [ ] mobile-cascader
- [ ] mobile-date-pickers
- [ ] mobile-date-time-pickers
- [ ] mobile-pickers
- [ ] mobil-picker-views
- [ ] mobile-time-pickers
- [ ] modals
- [ ] navigation-drawers
- [ ] not-grouped
- [ ] overlays
- [ ] pagination
- [ ] Pickers
- [ ] date-pickers
- [ ] date-pickers-month
- [ ] time-pickers
- [ ] popup-service
- [ ] progress
- [ ] progress-circular
- [ ] progress-linear
- [ ] ratings
- [ ] sheets
- [ ] skeleton-loaders
- [ ] snackbars
- [ ] steppers
- [ ] subheaders
- [ ] tables
- [ ] data-iterators
- [ ] data-tables
- [ ] simple-tables
- [ ] tabs
- [ ] timelines
- [ ] toast
- [ ] tooltips
- [ ] treeview
- [ ] virtual-scroll
| non_main | masa blazor new document task list masa blazor新文档功能清单 以下是剩余的任务列表,这将每天更新,所以要注意变化。 the following is the list of remaining tasks which will be updated daily so pay attention to changes 待办事项列表 to do list 文档框架核心 document framework core 左侧导航 left navigation 导航内容 navigation content 介绍 introduction 快速入门 getting started 特性 features 样式和动画 styles and animations 关于 about 功能和样式 function and style 版本切换 version switching 样式还原 style restore 和顶部导航联动 linkage with top navigation 国际化 导航标签 navigation label 顶部导航 top navigation 导航内容 navigation content 文档中心 document center 新手入门 getting started pro 博客 blog 社区 community 官网 official website 开源地址链接 功能和样式 function and style 样式还原 style restore 和左侧导航联动 导航标签 navigation label 全文检索 algolia full text retrieval algolia 语言切换 language switching 设置 settings 右侧导航 right navigation 对接github(issues)数据 docking github issues data 目录标签 catalog label 赞助商 sponsor 样式还原 style restore ui组件 当满足以下条件时,组件文档被视为已完成: 每个组件api文档中的每个属性、事件、 。 the component document is considered completed when the following conditions are met each attribute event slot etc in each component api document has a corresponding description and the api document supports switching alerts application aspect ratios avatars badges banners bars app bars toolbars system bars block text borders bottom navigation bottom sheets breadcrumbs buttons cards carousels chips copyable text cron dialogs dividers drag zone drawers echarts editor error handler expansion panels floating action buttons footers form inputs and ontrols autocomplete cascaders checkboxes file inputs forms otp input radio range sliders selects sliders switches textareas text fields grids groups button groups chip groups item groups list item groups slide groups windows hover icons image captcha images infinite scroll lists markdown menus mobiles mobile cascader mobile date pickers mobile date time pickers mobile pickers mobil picker views mobile time pickers modals navigation drawers not grouped overlays pagination pickers date pickers date pickers month time pickers popup service progress progress circular progress linear ratings sheets skeleton loaders snackbars steppers subheaders tables data iterators data tables simple tables tabs timelines toast tooltips treeview virtual scroll | 0 |
17,023 | 23,456,956,033 | IssuesEvent | 2022-08-16 09:42:15 | ISID/iPLAss | https://api.github.com/repos/ISID/iPLAss | closed | OracleRdbAdapterのuseFetchFirstClauseのデフォルト値をtrueに変更 | refactoring compatibility notes | OracleRdbAdapterのuseFetchFirstClauseのデフォルト値をtrueにする。
新規構築で11gを利用することはほぼないと思われる。
### Compatibility notes
引き続きOracle 11gを利用する場合、OracleRdbAdapterのuseFetchFirstClauseの設定値を明示的にfalseに設定する必要があります。
| True | OracleRdbAdapterのuseFetchFirstClauseのデフォルト値をtrueに変更 - OracleRdbAdapterのuseFetchFirstClauseのデフォルト値をtrueにする。
新規構築で11gを利用することはほぼないと思われる。
### Compatibility notes
引き続きOracle 11gを利用する場合、OracleRdbAdapterのuseFetchFirstClauseの設定値を明示的にfalseに設定する必要があります。
| non_main | oraclerdbadapterのusefetchfirstclauseのデフォルト値をtrueに変更 oraclerdbadapterのusefetchfirstclauseのデフォルト値をtrueにする。 。 compatibility notes 引き続きoracle 、oraclerdbadapterのusefetchfirstclauseの設定値を明示的にfalseに設定する必要があります。 | 0 |
5,544 | 27,748,110,412 | IssuesEvent | 2023-03-15 18:29:59 | centerofci/mathesar | https://api.github.com/repos/centerofci/mathesar | closed | Show edit exploration breadcrumb as a child of saved exploration item instead of the direct child of the schema | work: frontend status: ready restricted: maintainers | ## Current
**Saved Exploration**
<img width="890" alt="Screenshot 2022-12-07 at 3 41 55 AM" src="https://user-images.githubusercontent.com/11032856/206034579-1f96f693-b717-4fb6-9085-13c0f4c40102.png">
**Editing Saved Exploration**
<img width="690" alt="Screenshot 2022-12-07 at 3 42 00 AM" src="https://user-images.githubusercontent.com/11032856/206034589-2571339f-740b-42ad-b7b7-92d6d3ad7e77.png">
## Expected
**Saved Exploration**
<img width="696" alt="Screenshot 2022-12-07 at 3 44 10 AM" src="https://user-images.githubusercontent.com/11032856/206034934-38e711e2-637a-4eba-902f-0a26c1d9cefe.png">
**Editing Saved Exploration**
<img width="869" alt="Screenshot 2022-12-07 at 3 44 03 AM" src="https://user-images.githubusercontent.com/11032856/206034974-2490feb4-5869-4051-aa32-e6ca36c0ecca.png">
Blocked on: https://github.com/centerofci/mathesar/issues/2030 | True | Show edit exploration breadcrumb as a child of saved exploration item instead of the direct child of the schema - ## Current
**Saved Exploration**
<img width="890" alt="Screenshot 2022-12-07 at 3 41 55 AM" src="https://user-images.githubusercontent.com/11032856/206034579-1f96f693-b717-4fb6-9085-13c0f4c40102.png">
**Editing Saved Exploration**
<img width="690" alt="Screenshot 2022-12-07 at 3 42 00 AM" src="https://user-images.githubusercontent.com/11032856/206034589-2571339f-740b-42ad-b7b7-92d6d3ad7e77.png">
## Expected
**Saved Exploration**
<img width="696" alt="Screenshot 2022-12-07 at 3 44 10 AM" src="https://user-images.githubusercontent.com/11032856/206034934-38e711e2-637a-4eba-902f-0a26c1d9cefe.png">
**Editing Saved Exploration**
<img width="869" alt="Screenshot 2022-12-07 at 3 44 03 AM" src="https://user-images.githubusercontent.com/11032856/206034974-2490feb4-5869-4051-aa32-e6ca36c0ecca.png">
Blocked on: https://github.com/centerofci/mathesar/issues/2030 | main | show edit exploration breadcrumb as a child of saved exploration item instead of the direct child of the schema current saved exploration img width alt screenshot at am src editing saved exploration img width alt screenshot at am src expected saved exploration img width alt screenshot at am src editing saved exploration img width alt screenshot at am src blocked on | 1 |
517,485 | 15,014,693,901 | IssuesEvent | 2021-02-01 07:05:40 | teamforus/general | https://api.github.com/repos/teamforus/general | closed | Can't do any changes to my product after I've checked the box of: no price or unlimited stock. What if there really is a change or I made a mistake? | Approval: Not requested Impact: Significant Priority: Must have Scope: Medium Status: Not Planned Urgency: Medium - Next 3 sprints project-100 | Learn more about change requests here: https://bit.ly/39CWeEE
### Requested by:
- @GerbenBosschieter
### Change description
After a provider adds a product and realises they made a mistake or just want to change something on a later moment they can't always do if the following checkboxes are checked:
- unlimited stock
- no price
Let them be able to change this. Greying it out visually after choosing one is obvious. But limiting them is not really user friendly.
| 1.0 | Can't do any changes to my product after I've checked the box of: no price or unlimited stock. What if there really is a change or I made a mistake? - Learn more about change requests here: https://bit.ly/39CWeEE
### Requested by:
- @GerbenBosschieter
### Change description
After a provider adds a product and realises they made a mistake or just want to change something on a later moment they can't always do if the following checkboxes are checked:
- unlimited stock
- no price
Let them be able to change this. Greying it out visually after choosing one is obvious. But limiting them is not really user friendly.
| non_main | can t do any changes to my product after i ve checked the box of no price or unlimited stock what if there really is a change or i made a mistake learn more about change requests here requested by gerbenbosschieter change description after a provider adds a product and realises they made a mistake or just want to change something on a later moment they can t always do if the following checkboxes are checked unlimited stock no price let them be able to change this greying it out visually after choosing one is obvious but limiting them is not really user friendly | 0 |
2,277 | 8,073,411,131 | IssuesEvent | 2018-08-06 19:09:46 | AadityaNair/ProjectNephos | https://api.github.com/repos/AadityaNair/ProjectNephos | opened | Validate user input. | enhancement maintainability | We currently assume that all inputs are correct and is directly pluggable to the program. That will never be the case.
We have two starting points.
1. The values provided in the config.
2. Options provided in the commandline.
This can be more than just format and structural validation. IP addresses can be validated to be actually pingable. | True | Validate user input. - We currently assume that all inputs are correct and is directly pluggable to the program. That will never be the case.
We have two starting points.
1. The values provided in the config.
2. Options provided in the commandline.
This can be more than just format and structural validation. IP addresses can be validated to be actually pingable. | main | validate user input we currently assume that all inputs are correct and is directly pluggable to the program that will never be the case we have two starting points the values provided in the config options provided in the commandline this can be more than just format and structural validation ip addresses can be validated to be actually pingable | 1 |
2,256 | 7,930,619,609 | IssuesEvent | 2018-07-06 19:39:42 | MDAnalysis/mdanalysis | https://api.github.com/repos/MDAnalysis/mdanalysis | opened | deprecate save() methods | Component-Analysis maintainability | In #1745 we decided to remove most of the `save()` methods in the analysis classes in 1.0.
These removals have to be deprecated in a preceding release.
# To be deprecated
Check methods once they have been deprecated.
- [ ] MDAnalysis/analysis/align.py: def save(self, rmsdfile):
- [ ] MDAnalysis/analysis/contacts.py: def save(self, outfile):
- [ ] MDAnalysis/analysis/diffusionmap.py: def save(self, filename):
- [ ] MDAnalysis/analysis/hbonds/hbond_analysis.py: def save_table(self, filename="hbond_table.pickle"):
- [ ] MDAnalysis/analysis/hbonds/hbond_autocorrel.py: def save_results(self, filename='hbond_autocorrel'):
- [ ] MDAnalysis/analysis/hbonds/wbridge_analysis.py: def save_table(self, filename="wbridge_table.pickle"):
- [ ] MDAnalysis/analysis/hole.py: def save(self, filename="hole.pickle"):
- [ ] MDAnalysis/analysis/lineardensity.py: def save(self, description='', form='txt'):
- [ ] MDAnalysis/analysis/lineardensity.py: def _savetxt(self, filename):
- [ ] MDAnalysis/analysis/lineardensity.py: def _savez(self, filename):
- [ ] MDAnalysis/analysis/psa.py: def save_result(self, filename=None):
- [ ] MDAnalysis/analysis/rms.py: def save(self, filename=None):
| True | deprecate save() methods - In #1745 we decided to remove most of the `save()` methods in the analysis classes in 1.0.
These removals have to be deprecated in a preceding release.
# To be deprecated
Check methods once they have been deprecated.
- [ ] MDAnalysis/analysis/align.py: def save(self, rmsdfile):
- [ ] MDAnalysis/analysis/contacts.py: def save(self, outfile):
- [ ] MDAnalysis/analysis/diffusionmap.py: def save(self, filename):
- [ ] MDAnalysis/analysis/hbonds/hbond_analysis.py: def save_table(self, filename="hbond_table.pickle"):
- [ ] MDAnalysis/analysis/hbonds/hbond_autocorrel.py: def save_results(self, filename='hbond_autocorrel'):
- [ ] MDAnalysis/analysis/hbonds/wbridge_analysis.py: def save_table(self, filename="wbridge_table.pickle"):
- [ ] MDAnalysis/analysis/hole.py: def save(self, filename="hole.pickle"):
- [ ] MDAnalysis/analysis/lineardensity.py: def save(self, description='', form='txt'):
- [ ] MDAnalysis/analysis/lineardensity.py: def _savetxt(self, filename):
- [ ] MDAnalysis/analysis/lineardensity.py: def _savez(self, filename):
- [ ] MDAnalysis/analysis/psa.py: def save_result(self, filename=None):
- [ ] MDAnalysis/analysis/rms.py: def save(self, filename=None):
| main | deprecate save methods in we decided to remove most of the save methods in the analysis classes in these removals have to be deprecated in a preceding release to be deprecated check methods once they have been deprecated mdanalysis analysis align py def save self rmsdfile mdanalysis analysis contacts py def save self outfile mdanalysis analysis diffusionmap py def save self filename mdanalysis analysis hbonds hbond analysis py def save table self filename hbond table pickle mdanalysis analysis hbonds hbond autocorrel py def save results self filename hbond autocorrel mdanalysis analysis hbonds wbridge analysis py def save table self filename wbridge table pickle mdanalysis analysis hole py def save self filename hole pickle mdanalysis analysis lineardensity py def save self description form txt mdanalysis analysis lineardensity py def savetxt self filename mdanalysis analysis lineardensity py def savez self filename mdanalysis analysis psa py def save result self filename none mdanalysis analysis rms py def save self filename none | 1 |
718,790 | 24,731,981,054 | IssuesEvent | 2022-10-20 18:24:54 | nasa/fprime | https://api.github.com/repos/nasa/fprime | closed | Add standard FPP types | enhancement High Priority Easy First Issue | | | |
|:---|:---|
|**_F´ Version_**| 3.0 |
|**_Affected Component_**| None |
---
## Feature Description
Add some common types that users could use. Things like:
ON, OFF (ex. a device)
HIGH, LOW (logic level)
OPEN, CLOSED (file, cover, etc)
IN, OUT (direction of flow)
ACTIVE, INACTIVE (behavior)
HEALTHY, SICK, FAILED (Device health)
## Rationale
Would avoid users defining them again and again.
| 1.0 | Add standard FPP types - | | |
|:---|:---|
|**_F´ Version_**| 3.0 |
|**_Affected Component_**| None |
---
## Feature Description
Add some common types that users could use. Things like:
ON, OFF (ex. a device)
HIGH, LOW (logic level)
OPEN, CLOSED (file, cover, etc)
IN, OUT (direction of flow)
ACTIVE, INACTIVE (behavior)
HEALTHY, SICK, FAILED (Device health)
## Rationale
Would avoid users defining them again and again.
| non_main | add standard fpp types f´ version affected component none feature description add some common types that users could use things like on off ex a device high low logic level open closed file cover etc in out direction of flow active inactive behavior healthy sick failed device health rationale would avoid users defining them again and again | 0 |
317,284 | 9,662,826,952 | IssuesEvent | 2019-05-20 21:59:32 | RobotLocomotion/drake | https://api.github.com/repos/RobotLocomotion/drake | opened | geometry: Isolate LCM dependency | priority: high team: dynamics type: bug | The `//multibody/plant:multibody_plant_code` depends on `//geometry:geometry_visualization`, and `//geometry:geometry_visualization` depends on `//lcm` -- oops, now MBP depends on LCM.
There is only one tiny function in `geometry_visulization.h` needed by MBP. We should carve out that function into some other file, either an existing one or a new one. | 1.0 | geometry: Isolate LCM dependency - The `//multibody/plant:multibody_plant_code` depends on `//geometry:geometry_visualization`, and `//geometry:geometry_visualization` depends on `//lcm` -- oops, now MBP depends on LCM.
There is only one tiny function in `geometry_visulization.h` needed by MBP. We should carve out that function into some other file, either an existing one or a new one. | non_main | geometry isolate lcm dependency the multibody plant multibody plant code depends on geometry geometry visualization and geometry geometry visualization depends on lcm oops now mbp depends on lcm there is only one tiny function in geometry visulization h needed by mbp we should carve out that function into some other file either an existing one or a new one | 0 |
80,012 | 15,338,861,382 | IssuesEvent | 2021-02-27 00:03:01 | adam-r-kowalski/lang | https://api.github.com/repos/adam-r-kowalski/lang | opened | stack alignment | codegen enhancement | Before calling a function the stack needs to be aligned to 16 bytes. Track all stack manipulation and ensure that when making a call, the stack is properly aligned by subtracting the correct number of bytes from the stack. A compensating action must be performed afterward to ensure popping the stack will give back the correct data. A stack of compensating actions should be maintained, so that they can be merged to a single operation. | 1.0 | stack alignment - Before calling a function the stack needs to be aligned to 16 bytes. Track all stack manipulation and ensure that when making a call, the stack is properly aligned by subtracting the correct number of bytes from the stack. A compensating action must be performed afterward to ensure popping the stack will give back the correct data. A stack of compensating actions should be maintained, so that they can be merged to a single operation. | non_main | stack alignment before calling a function the stack needs to be aligned to bytes track all stack manipulation and ensure that when making a call the stack is properly aligned by subtracting the correct number of bytes from the stack a compensating action must be performed afterward to ensure popping the stack will give back the correct data a stack of compensating actions should be maintained so that they can be merged to a single operation | 0 |
12,386 | 3,268,382,692 | IssuesEvent | 2015-10-23 11:07:35 | payara/Payara | https://api.github.com/repos/payara/Payara | closed | Possible WebappClassLoader leak (permgen issue) | Test Case Required | While developing and regularly deploying instances on my local server, I am encountering OutOfMemory errors on the PermGen side of things. After examining the jvm with jvisualvm I can confirm that each redeploy causes an increment in the permgen size and forcing GC does not alleviate the problem.
Even with JDK 1.7 options -XX:+CMSPermGenSweepingEnabled and -XX:+CMSClassUnloadingEnabled enabled, the permgen size does not go down.
Close inspection via heapdump shows that for every deploy a new WebappClassloader is created(which is normal) but existing ones do not disappear(started flag is at false). and thus the heap continues to grow.

Heapdump can be downloaded from https://www.dropbox.com/s/o10i4394g2aq5l9/heapdump-payara.zip?dl=0 | 1.0 | Possible WebappClassLoader leak (permgen issue) - While developing and regularly deploying instances on my local server, I am encountering OutOfMemory errors on the PermGen side of things. After examining the jvm with jvisualvm I can confirm that each redeploy causes an increment in the permgen size and forcing GC does not alleviate the problem.
Even with JDK 1.7 options -XX:+CMSPermGenSweepingEnabled and -XX:+CMSClassUnloadingEnabled enabled, the permgen size does not go down.
Close inspection via heapdump shows that for every deploy a new WebappClassloader is created(which is normal) but existing ones do not disappear(started flag is at false). and thus the heap continues to grow.

Heapdump can be downloaded from https://www.dropbox.com/s/o10i4394g2aq5l9/heapdump-payara.zip?dl=0 | non_main | possible webappclassloader leak permgen issue while developing and regularly deploying instances on my local server i am encountering outofmemory errors on the permgen side of things after examining the jvm with jvisualvm i can confirm that each redeploy causes an increment in the permgen size and forcing gc does not alleviate the problem even with jdk options xx cmspermgensweepingenabled and xx cmsclassunloadingenabled enabled the permgen size does not go down close inspection via heapdump shows that for every deploy a new webappclassloader is created which is normal but existing ones do not disappear started flag is at false and thus the heap continues to grow heapdump can be downloaded from | 0 |
5,148 | 26,247,227,595 | IssuesEvent | 2023-01-05 16:10:01 | centerofci/mathesar | https://api.github.com/repos/centerofci/mathesar | opened | Allow deleting a record with CASCADE | type: enhancement work: backend work: frontend status: draft restricted: maintainers | ## Problem
- You can't delete a record which is referenced by other records
## Desired outcome
- We should give users a way to delete such records
## Design challenges
- At what point does the user make the decision to use CASCADE or not use CASCADE?
- How does the user communicate that choice to Mathesar?
- How does Mathesar communicate the behavior of CASCADE to the user?
| True | Allow deleting a record with CASCADE - ## Problem
- You can't delete a record which is referenced by other records
## Desired outcome
- We should give users a way to delete such records
## Design challenges
- At what point does the user make the decision to use CASCADE or not use CASCADE?
- How does the user communicate that choice to Mathesar?
- How does Mathesar communicate the behavior of CASCADE to the user?
| main | allow deleting a record with cascade problem you can t delete a record which is referenced by other records desired outcome we should give users a way to delete such records design challenges at what point does the user make the decision to use cascade or not use cascade how does the user communicate that choice to mathesar how does mathesar communicate the behavior of cascade to the user | 1 |
4,558 | 23,727,528,612 | IssuesEvent | 2022-08-30 21:09:15 | aws/aws-sam-cli | https://api.github.com/repos/aws/aws-sam-cli | closed | SAM deploy doesn't set environment variables | type/ux type/feedback maintainer/need-followup | ### Description
When using AWS SAM for local development, I can introduce environment variables by setting them in the template with no value, and then defining them in my environment. However, when I go to deploy, the environment variables do not appear to be inserted by `sam package` or `sam deploy`, and I get the following error on deploy:
```
Failed to create the changeset: Waiter ChangeSetCreateComplete failed: Waiter encountered a terminal failure state Status: FAILED. Reason: [/Resources/GeneratePlan/Type/Environment/Variables/SECRET_ACCESS_KEY] 'null' values are not allowed in templates
```
Where `SECRET_ACCESS_KEY` is one of my environment variables. I cannot find any documentation detailing how to deploy projects with environment variables, either by having them defined in my environment or providing them in an alternate config.
I don't want to add the environment variables to my `template.yml` directly because this is stored in Git, and I don't want to edit them manually into the `packaged.yml` file each time between the `package` and `deploy` steps as that's cumbersome.
I haven't seen any steps in the documentation or similar issues, so I presume this is either an edge case bug or I am just missing something simple (in which case I might file this as a documentation bug) 😄
### Steps to reproduce
The following config is a minimal excerpt from mine:
```
AWSTemplateFormatVersion: '2010-09-09'
Transform: AWS::Serverless-2016-10-31
Globals:
Function:
Environment:
Variables:
SECRET_ACCESS_KEY:
Resources:
AnswerChallenge:
Type: "AWS::Serverless::Function"
Properties:
Runtime: nodejs8.10
Handler: build/functions/answerChallenge.default
CodeUri: ./
Policies: AmazonDynamoDBFullAccess
Events:
GetRequest:
Type: Api
Properties:
Path: /event
Method: get
```
### Observed result
When I run `sam start-api` with `SECRET_ACCESS_KEY` defined, the lambda works as expected. When I attempt to deploy with `sam package` and `sam deploy`, I receive an error about undefined variables.
### Additional environment details (Ex: Windows, Mac, Amazon Linux etc)
1. OS: MacOS
2. `sam --version`: 0.11 | True | SAM deploy doesn't set environment variables - ### Description
When using AWS SAM for local development, I can introduce environment variables by setting them in the template with no value, and then defining them in my environment. However, when I go to deploy, the environment variables do not appear to be inserted by `sam package` or `sam deploy`, and I get the following error on deploy:
```
Failed to create the changeset: Waiter ChangeSetCreateComplete failed: Waiter encountered a terminal failure state Status: FAILED. Reason: [/Resources/GeneratePlan/Type/Environment/Variables/SECRET_ACCESS_KEY] 'null' values are not allowed in templates
```
Where `SECRET_ACCESS_KEY` is one of my environment variables. I cannot find any documentation detailing how to deploy projects with environment variables, either by having them defined in my environment or providing them in an alternate config.
I don't want to add the environment variables to my `template.yml` directly because this is stored in Git, and I don't want to edit them manually into the `packaged.yml` file each time between the `package` and `deploy` steps as that's cumbersome.
I haven't seen any steps in the documentation or similar issues, so I presume this is either an edge case bug or I am just missing something simple (in which case I might file this as a documentation bug) 😄
### Steps to reproduce
The following config is a minimal excerpt from mine:
```
AWSTemplateFormatVersion: '2010-09-09'
Transform: AWS::Serverless-2016-10-31
Globals:
Function:
Environment:
Variables:
SECRET_ACCESS_KEY:
Resources:
AnswerChallenge:
Type: "AWS::Serverless::Function"
Properties:
Runtime: nodejs8.10
Handler: build/functions/answerChallenge.default
CodeUri: ./
Policies: AmazonDynamoDBFullAccess
Events:
GetRequest:
Type: Api
Properties:
Path: /event
Method: get
```
### Observed result
When I run `sam start-api` with `SECRET_ACCESS_KEY` defined, the lambda works as expected. When I attempt to deploy with `sam package` and `sam deploy`, I receive an error about undefined variables.
### Additional environment details (Ex: Windows, Mac, Amazon Linux etc)
1. OS: MacOS
2. `sam --version`: 0.11 | main | sam deploy doesn t set environment variables description when using aws sam for local development i can introduce environment variables by setting them in the template with no value and then defining them in my environment however when i go to deploy the environment variables do not appear to be inserted by sam package or sam deploy and i get the following error on deploy failed to create the changeset waiter changesetcreatecomplete failed waiter encountered a terminal failure state status failed reason null values are not allowed in templates where secret access key is one of my environment variables i cannot find any documentation detailing how to deploy projects with environment variables either by having them defined in my environment or providing them in an alternate config i don t want to add the environment variables to my template yml directly because this is stored in git and i don t want to edit them manually into the packaged yml file each time between the package and deploy steps as that s cumbersome i haven t seen any steps in the documentation or similar issues so i presume this is either an edge case bug or i am just missing something simple in which case i might file this as a documentation bug 😄 steps to reproduce the following config is a minimal excerpt from mine awstemplateformatversion transform aws serverless globals function environment variables secret access key resources answerchallenge type aws serverless function properties runtime handler build functions answerchallenge default codeuri policies amazondynamodbfullaccess events getrequest type api properties path event method get observed result when i run sam start api with secret access key defined the lambda works as expected when i attempt to deploy with sam package and sam deploy i receive an error about undefined variables additional environment details ex windows mac amazon linux etc os macos sam version | 1 |
215,499 | 16,605,951,009 | IssuesEvent | 2021-06-02 03:50:14 | facebookresearch/detectron2 | https://api.github.com/repos/facebookresearch/detectron2 | closed | Classification yaml missing. | documentation | After the push of https://github.com/facebookresearch/detectron2/commit/76963c909120d8ca046a18f5f399d5dc1b8a480f
torchvision_imagenet_R_50.py has been added to detectron2/configs/Misc/
However, this is not a yaml file but a py file.
A classification yaml file is still missing. | 1.0 | Classification yaml missing. - After the push of https://github.com/facebookresearch/detectron2/commit/76963c909120d8ca046a18f5f399d5dc1b8a480f
torchvision_imagenet_R_50.py has been added to detectron2/configs/Misc/
However, this is not a yaml file but a py file.
A classification yaml file is still missing. | non_main | classification yaml missing after the push of torchvision imagenet r py has been added to configs misc however this is not a yaml file but a py file a classification yaml file is still missing | 0 |
1,435 | 6,223,458,703 | IssuesEvent | 2017-07-10 11:59:37 | chocolatey/chocolatey-package-requests | https://api.github.com/repos/chocolatey/chocolatey-package-requests | opened | RFM - PandaFreeAntivirus | Status: Available For Maintainer(s) | The maintainers from the [PandaFreeAntivirus](https://chocolatey.org/packages/PandaFreeAntivirus) recently decided to stop maintaining this package and is requesting a new maintainer for it.
The source of the package is available [here](https://github.com/chocolatey/chocolatey-coreteampackages/tree/a1202463831ee4198950c04c9fac4cdf0816c46e/automatic/pandafreeantivirus). | True | RFM - PandaFreeAntivirus - The maintainers from the [PandaFreeAntivirus](https://chocolatey.org/packages/PandaFreeAntivirus) recently decided to stop maintaining this package and is requesting a new maintainer for it.
The source of the package is available [here](https://github.com/chocolatey/chocolatey-coreteampackages/tree/a1202463831ee4198950c04c9fac4cdf0816c46e/automatic/pandafreeantivirus). | main | rfm pandafreeantivirus the maintainers from the recently decided to stop maintaining this package and is requesting a new maintainer for it the source of the package is available | 1 |
2,438 | 8,634,896,218 | IssuesEvent | 2018-11-22 19:02:17 | coq-community/manifesto | https://api.github.com/repos/coq-community/manifesto | opened | Proposal to add SyDRec | maintainer-wanted | ## Move a project to coq-community ##
**Project name:** SyDRec
**Initial author(s):** [Simon Robillard](https://github.com/simonr89)
**Current URL:** https://github.com/simonr89/SyDRec
**Kind:** OCaml plugin
**License:** CeCILL-C
**Description:** Plugin that allows generating catamorphisms and accompanying fusion lemmas from inductive types. This provides support for the "derivation-style" program development advocated by Richard Bird and others (see the book Algebra of Programming). The theory and implementation is described in the paper [Catamorphism Generation and Fusion Using Coq](https://doi.org/10.1109/SYNASC.2014.32).
**Status:** Appears unmaintained. Last supported version of Coq is 8.4.
**New maintainer:** looking for a volunteer
| True | Proposal to add SyDRec - ## Move a project to coq-community ##
**Project name:** SyDRec
**Initial author(s):** [Simon Robillard](https://github.com/simonr89)
**Current URL:** https://github.com/simonr89/SyDRec
**Kind:** OCaml plugin
**License:** CeCILL-C
**Description:** Plugin that allows generating catamorphisms and accompanying fusion lemmas from inductive types. This provides support for the "derivation-style" program development advocated by Richard Bird and others (see the book Algebra of Programming). The theory and implementation is described in the paper [Catamorphism Generation and Fusion Using Coq](https://doi.org/10.1109/SYNASC.2014.32).
**Status:** Appears unmaintained. Last supported version of Coq is 8.4.
**New maintainer:** looking for a volunteer
| main | proposal to add sydrec move a project to coq community project name sydrec initial author s current url kind ocaml plugin license cecill c description plugin that allows generating catamorphisms and accompanying fusion lemmas from inductive types this provides support for the derivation style program development advocated by richard bird and others see the book algebra of programming the theory and implementation is described in the paper status appears unmaintained last supported version of coq is new maintainer looking for a volunteer | 1 |
98,237 | 16,361,469,924 | IssuesEvent | 2021-05-14 10:07:50 | Galaxy-Software-Service/Maven_Pom_Demo | https://api.github.com/repos/Galaxy-Software-Service/Maven_Pom_Demo | opened | CVE-2013-2186 (High) detected in commons-fileupload-1.3.jar | security vulnerability | ## CVE-2013-2186 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-fileupload-1.3.jar</b></p></summary>
<p>The FileUpload component provides a simple yet flexible means of adding support for multipart
file upload functionality to servlets and web applications.</p>
<p>Path to dependency file: Maven_Pom_Demo/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-fileupload/commons-fileupload/1.3/commons-fileupload-1.3.jar</p>
<p>
Dependency Hierarchy:
- struts2-core-2.3.15.jar (Root Library)
- :x: **commons-fileupload-1.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Galaxy-Software-Service/Maven_Pom_Demo/commit/69cce4bac0c1b37088c48547695b174bd6149c5c">69cce4bac0c1b37088c48547695b174bd6149c5c</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The DiskFileItem class in Apache Commons FileUpload, as used in Red Hat JBoss BRMS 5.3.1; JBoss Portal 4.3 CP07, 5.2.2, and 6.0.0; and Red Hat JBoss Web Server 1.0.2 allows remote attackers to write to arbitrary files via a NULL byte in a file name in a serialized instance.
<p>Publish Date: 2013-10-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-2186>CVE-2013-2186</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2013-2186">https://nvd.nist.gov/vuln/detail/CVE-2013-2186</a></p>
<p>Release Date: 2019-04-08</p>
<p>Fix Resolution: 1.3.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"commons-fileupload","packageName":"commons-fileupload","packageVersion":"1.3","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.struts:struts2-core:2.3.15;commons-fileupload:commons-fileupload:1.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.3.1"}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2013-2186","vulnerabilityDetails":"The DiskFileItem class in Apache Commons FileUpload, as used in Red Hat JBoss BRMS 5.3.1; JBoss Portal 4.3 CP07, 5.2.2, and 6.0.0; and Red Hat JBoss Web Server 1.0.2 allows remote attackers to write to arbitrary files via a NULL byte in a file name in a serialized instance.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-2186","cvss2Severity":"high","cvss2Score":"7.5","extraData":{}}</REMEDIATE> --> | True | CVE-2013-2186 (High) detected in commons-fileupload-1.3.jar - ## CVE-2013-2186 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-fileupload-1.3.jar</b></p></summary>
<p>The FileUpload component provides a simple yet flexible means of adding support for multipart
file upload functionality to servlets and web applications.</p>
<p>Path to dependency file: Maven_Pom_Demo/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-fileupload/commons-fileupload/1.3/commons-fileupload-1.3.jar</p>
<p>
Dependency Hierarchy:
- struts2-core-2.3.15.jar (Root Library)
- :x: **commons-fileupload-1.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Galaxy-Software-Service/Maven_Pom_Demo/commit/69cce4bac0c1b37088c48547695b174bd6149c5c">69cce4bac0c1b37088c48547695b174bd6149c5c</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The DiskFileItem class in Apache Commons FileUpload, as used in Red Hat JBoss BRMS 5.3.1; JBoss Portal 4.3 CP07, 5.2.2, and 6.0.0; and Red Hat JBoss Web Server 1.0.2 allows remote attackers to write to arbitrary files via a NULL byte in a file name in a serialized instance.
<p>Publish Date: 2013-10-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-2186>CVE-2013-2186</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2013-2186">https://nvd.nist.gov/vuln/detail/CVE-2013-2186</a></p>
<p>Release Date: 2019-04-08</p>
<p>Fix Resolution: 1.3.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"commons-fileupload","packageName":"commons-fileupload","packageVersion":"1.3","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.struts:struts2-core:2.3.15;commons-fileupload:commons-fileupload:1.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.3.1"}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2013-2186","vulnerabilityDetails":"The DiskFileItem class in Apache Commons FileUpload, as used in Red Hat JBoss BRMS 5.3.1; JBoss Portal 4.3 CP07, 5.2.2, and 6.0.0; and Red Hat JBoss Web Server 1.0.2 allows remote attackers to write to arbitrary files via a NULL byte in a file name in a serialized instance.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-2186","cvss2Severity":"high","cvss2Score":"7.5","extraData":{}}</REMEDIATE> --> | non_main | cve high detected in commons fileupload jar cve high severity vulnerability vulnerable library commons fileupload jar the fileupload component provides a simple yet flexible means of adding support for multipart file upload functionality to servlets and web applications path to dependency file maven pom demo pom xml path to vulnerable library home wss scanner repository commons fileupload commons fileupload commons fileupload jar dependency hierarchy core jar root library x commons fileupload jar vulnerable library found in head commit a href found in base branch main vulnerability details the diskfileitem class in apache commons fileupload as used in red hat jboss brms jboss portal and and red hat jboss web server allows remote attackers to write to arbitrary files via a null byte in a file name in a serialized instance publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org apache struts core commons fileupload commons fileupload isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails the diskfileitem class in apache commons fileupload as used in red hat jboss brms jboss portal and and red hat jboss web server allows remote attackers to write to arbitrary files via a null byte in a file name in a serialized instance vulnerabilityurl | 0 |
982 | 4,746,549,521 | IssuesEvent | 2016-10-21 11:38:04 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | Feature Idea : cloudformation "describe" state | affects_2.0 aws cloud feature_idea waiting_on_maintainer | What do people thing about "describe" or "available" state for cloudformation module. I'm happy to add it in and send pull req I just want to make sure it will get accepted before I start it :)
**Use case:**
build stack in separate playbook/ansible run, and then I would like to use it like
```YML
- name: Get MyStack tier
cloudformation:
aws_access_key: "{{ aws.access_key }}"
aws_secret_key: "{{ aws.secret_key }}"
stack_name: my-stack-name
state: available
register: mystack_data
- name: use {{ mystack_data.outputs.* }} in some awesome ways
```
I really don't want to use lookup plugins, as it's a bit ugly and limited to specify aws secrets and keys per run. Also I need to run lookup for each stack output. | True | Feature Idea : cloudformation "describe" state - What do people thing about "describe" or "available" state for cloudformation module. I'm happy to add it in and send pull req I just want to make sure it will get accepted before I start it :)
**Use case:**
build stack in separate playbook/ansible run, and then I would like to use it like
```YML
- name: Get MyStack tier
cloudformation:
aws_access_key: "{{ aws.access_key }}"
aws_secret_key: "{{ aws.secret_key }}"
stack_name: my-stack-name
state: available
register: mystack_data
- name: use {{ mystack_data.outputs.* }} in some awesome ways
```
I really don't want to use lookup plugins, as it's a bit ugly and limited to specify aws secrets and keys per run. Also I need to run lookup for each stack output. | main | feature idea cloudformation describe state what do people thing about describe or available state for cloudformation module i m happy to add it in and send pull req i just want to make sure it will get accepted before i start it use case build stack in separate playbook ansible run and then i would like to use it like yml name get mystack tier cloudformation aws access key aws access key aws secret key aws secret key stack name my stack name state available register mystack data name use mystack data outputs in some awesome ways i really don t want to use lookup plugins as it s a bit ugly and limited to specify aws secrets and keys per run also i need to run lookup for each stack output | 1 |
136,524 | 5,284,243,618 | IssuesEvent | 2017-02-07 23:38:47 | imrogues/abstract | https://api.github.com/repos/imrogues/abstract | opened | Representing Objects | [priority] medium [status] accepted [type] feature | ### Description
Define what `eval` function returns.
---
### Issue Checklist
- [ ] Foundations of Object System
- [ ] Integers
- [ ] Booleans
- [ ] Null
All issues in milestone: [4 Evaluation](https://github.com/imrogues/abstract/milestone/4)
---
### Assignees
- [ ] Final assign @imrogues | 1.0 | Representing Objects - ### Description
Define what `eval` function returns.
---
### Issue Checklist
- [ ] Foundations of Object System
- [ ] Integers
- [ ] Booleans
- [ ] Null
All issues in milestone: [4 Evaluation](https://github.com/imrogues/abstract/milestone/4)
---
### Assignees
- [ ] Final assign @imrogues | non_main | representing objects description define what eval function returns issue checklist foundations of object system integers booleans null all issues in milestone assignees final assign imrogues | 0 |
4,265 | 6,824,729,253 | IssuesEvent | 2017-11-08 07:47:46 | general-language-syntax/GLS | https://api.github.com/repos/general-language-syntax/GLS | closed | { characters within a line confuse the parser | bug help wanted roundtripping requirement | Given this GLS:
```gls
print : { concatenate : "{" "a" }
```
It should print fine (`console.log("{" + "a");` in JS/TS). Unfortunately it gives an error:
```
Could not find end for '{' starting at position 8.
```
The issue is that `GlsParser.ts` isn't smart about when ranges of text within special characters start or stop.
| 1.0 | { characters within a line confuse the parser - Given this GLS:
```gls
print : { concatenate : "{" "a" }
```
It should print fine (`console.log("{" + "a");` in JS/TS). Unfortunately it gives an error:
```
Could not find end for '{' starting at position 8.
```
The issue is that `GlsParser.ts` isn't smart about when ranges of text within special characters start or stop.
| non_main | characters within a line confuse the parser given this gls gls print concatenate a it should print fine console log a in js ts unfortunately it gives an error could not find end for starting at position the issue is that glsparser ts isn t smart about when ranges of text within special characters start or stop | 0 |
118,495 | 17,594,163,426 | IssuesEvent | 2021-08-17 01:02:05 | doc-ai/tensorflow | https://api.github.com/repos/doc-ai/tensorflow | opened | CVE-2021-29530 (High) detected in tensorflow-2.0.0b1-cp36-cp36m-manylinux1_x86_64.whl | security vulnerability | ## CVE-2021-29530 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-2.0.0b1-cp36-cp36m-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/29/6c/2c9a5c4d095c63c2fb37d20def0e4f92685f7aee9243d6aae25862694fd1/tensorflow-2.0.0b1-cp36-cp36m-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/29/6c/2c9a5c4d095c63c2fb37d20def0e4f92685f7aee9243d6aae25862694fd1/tensorflow-2.0.0b1-cp36-cp36m-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: tensorflow/tensorflow/lite/micro/examples/magic_wand/train/requirements.txt</p>
<p>Path to vulnerable library: tensorflow/tensorflow/lite/micro/examples/magic_wand/train/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-2.0.0b1-cp36-cp36m-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an end-to-end open source platform for machine learning. An attacker can trigger a null pointer dereference by providing an invalid `permutation` to `tf.raw_ops.SparseMatrixSparseCholesky`. This is because the implementation(https://github.com/tensorflow/tensorflow/blob/080f1d9e257589f78b3ffb75debf584168aa6062/tensorflow/core/kernels/sparse/sparse_cholesky_op.cc#L85-L86) fails to properly validate the input arguments. Although `ValidateInputs` is called and there are checks in the body of this function, the code proceeds to the next line in `ValidateInputs` since `OP_REQUIRES`(https://github.com/tensorflow/tensorflow/blob/080f1d9e257589f78b3ffb75debf584168aa6062/tensorflow/core/framework/op_requires.h#L41-L48) is a macro that only exits the current function. Thus, the first validation condition that fails in `ValidateInputs` will cause an early return from that function. However, the caller will continue execution from the next line. The fix is to either explicitly check `context->status()` or to convert `ValidateInputs` to return a `Status`. The fix will be included in TensorFlow 2.5.0. We will also cherrypick this commit on TensorFlow 2.4.2, TensorFlow 2.3.3, TensorFlow 2.2.3 and TensorFlow 2.1.4, as these are also affected and still in supported range.
<p>Publish Date: 2021-05-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29530>CVE-2021-29530</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-xcwj-wfcm-m23c">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-xcwj-wfcm-m23c</a></p>
<p>Release Date: 2021-05-14</p>
<p>Fix Resolution: tensorflow - 2.5.0, tensorflow-cpu - 2.5.0, tensorflow-gpu - 2.5.0</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"tensorflow","packageVersion":"2.0.0b1","packageFilePaths":["/tensorflow/lite/micro/examples/magic_wand/train/requirements.txt"],"isTransitiveDependency":false,"dependencyTree":"tensorflow:2.0.0b1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"tensorflow - 2.5.0, tensorflow-cpu - 2.5.0, tensorflow-gpu - 2.5.0"}],"baseBranches":[],"vulnerabilityIdentifier":"CVE-2021-29530","vulnerabilityDetails":"TensorFlow is an end-to-end open source platform for machine learning. An attacker can trigger a null pointer dereference by providing an invalid `permutation` to `tf.raw_ops.SparseMatrixSparseCholesky`. This is because the implementation(https://github.com/tensorflow/tensorflow/blob/080f1d9e257589f78b3ffb75debf584168aa6062/tensorflow/core/kernels/sparse/sparse_cholesky_op.cc#L85-L86) fails to properly validate the input arguments. Although `ValidateInputs` is called and there are checks in the body of this function, the code proceeds to the next line in `ValidateInputs` since `OP_REQUIRES`(https://github.com/tensorflow/tensorflow/blob/080f1d9e257589f78b3ffb75debf584168aa6062/tensorflow/core/framework/op_requires.h#L41-L48) is a macro that only exits the current function. Thus, the first validation condition that fails in `ValidateInputs` will cause an early return from that function. However, the caller will continue execution from the next line. The fix is to either explicitly check `context-\u003estatus()` or to convert `ValidateInputs` to return a `Status`. The fix will be included in TensorFlow 2.5.0. We will also cherrypick this commit on TensorFlow 2.4.2, TensorFlow 2.3.3, TensorFlow 2.2.3 and TensorFlow 2.1.4, as these are also affected and still in supported range.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29530","cvss3Severity":"high","cvss3Score":"7.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-29530 (High) detected in tensorflow-2.0.0b1-cp36-cp36m-manylinux1_x86_64.whl - ## CVE-2021-29530 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-2.0.0b1-cp36-cp36m-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/29/6c/2c9a5c4d095c63c2fb37d20def0e4f92685f7aee9243d6aae25862694fd1/tensorflow-2.0.0b1-cp36-cp36m-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/29/6c/2c9a5c4d095c63c2fb37d20def0e4f92685f7aee9243d6aae25862694fd1/tensorflow-2.0.0b1-cp36-cp36m-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: tensorflow/tensorflow/lite/micro/examples/magic_wand/train/requirements.txt</p>
<p>Path to vulnerable library: tensorflow/tensorflow/lite/micro/examples/magic_wand/train/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-2.0.0b1-cp36-cp36m-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an end-to-end open source platform for machine learning. An attacker can trigger a null pointer dereference by providing an invalid `permutation` to `tf.raw_ops.SparseMatrixSparseCholesky`. This is because the implementation(https://github.com/tensorflow/tensorflow/blob/080f1d9e257589f78b3ffb75debf584168aa6062/tensorflow/core/kernels/sparse/sparse_cholesky_op.cc#L85-L86) fails to properly validate the input arguments. Although `ValidateInputs` is called and there are checks in the body of this function, the code proceeds to the next line in `ValidateInputs` since `OP_REQUIRES`(https://github.com/tensorflow/tensorflow/blob/080f1d9e257589f78b3ffb75debf584168aa6062/tensorflow/core/framework/op_requires.h#L41-L48) is a macro that only exits the current function. Thus, the first validation condition that fails in `ValidateInputs` will cause an early return from that function. However, the caller will continue execution from the next line. The fix is to either explicitly check `context->status()` or to convert `ValidateInputs` to return a `Status`. The fix will be included in TensorFlow 2.5.0. We will also cherrypick this commit on TensorFlow 2.4.2, TensorFlow 2.3.3, TensorFlow 2.2.3 and TensorFlow 2.1.4, as these are also affected and still in supported range.
<p>Publish Date: 2021-05-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29530>CVE-2021-29530</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-xcwj-wfcm-m23c">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-xcwj-wfcm-m23c</a></p>
<p>Release Date: 2021-05-14</p>
<p>Fix Resolution: tensorflow - 2.5.0, tensorflow-cpu - 2.5.0, tensorflow-gpu - 2.5.0</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"tensorflow","packageVersion":"2.0.0b1","packageFilePaths":["/tensorflow/lite/micro/examples/magic_wand/train/requirements.txt"],"isTransitiveDependency":false,"dependencyTree":"tensorflow:2.0.0b1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"tensorflow - 2.5.0, tensorflow-cpu - 2.5.0, tensorflow-gpu - 2.5.0"}],"baseBranches":[],"vulnerabilityIdentifier":"CVE-2021-29530","vulnerabilityDetails":"TensorFlow is an end-to-end open source platform for machine learning. An attacker can trigger a null pointer dereference by providing an invalid `permutation` to `tf.raw_ops.SparseMatrixSparseCholesky`. This is because the implementation(https://github.com/tensorflow/tensorflow/blob/080f1d9e257589f78b3ffb75debf584168aa6062/tensorflow/core/kernels/sparse/sparse_cholesky_op.cc#L85-L86) fails to properly validate the input arguments. Although `ValidateInputs` is called and there are checks in the body of this function, the code proceeds to the next line in `ValidateInputs` since `OP_REQUIRES`(https://github.com/tensorflow/tensorflow/blob/080f1d9e257589f78b3ffb75debf584168aa6062/tensorflow/core/framework/op_requires.h#L41-L48) is a macro that only exits the current function. Thus, the first validation condition that fails in `ValidateInputs` will cause an early return from that function. However, the caller will continue execution from the next line. The fix is to either explicitly check `context-\u003estatus()` or to convert `ValidateInputs` to return a `Status`. The fix will be included in TensorFlow 2.5.0. We will also cherrypick this commit on TensorFlow 2.4.2, TensorFlow 2.3.3, TensorFlow 2.2.3 and TensorFlow 2.1.4, as these are also affected and still in supported range.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29530","cvss3Severity":"high","cvss3Score":"7.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"High"},"extraData":{}}</REMEDIATE> --> | non_main | cve high detected in tensorflow whl cve high severity vulnerability vulnerable library tensorflow whl tensorflow is an open source machine learning framework for everyone library home page a href path to dependency file tensorflow tensorflow lite micro examples magic wand train requirements txt path to vulnerable library tensorflow tensorflow lite micro examples magic wand train requirements txt dependency hierarchy x tensorflow whl vulnerable library vulnerability details tensorflow is an end to end open source platform for machine learning an attacker can trigger a null pointer dereference by providing an invalid permutation to tf raw ops sparsematrixsparsecholesky this is because the implementation fails to properly validate the input arguments although validateinputs is called and there are checks in the body of this function the code proceeds to the next line in validateinputs since op requires is a macro that only exits the current function thus the first validation condition that fails in validateinputs will cause an early return from that function however the caller will continue execution from the next line the fix is to either explicitly check context status or to convert validateinputs to return a status the fix will be included in tensorflow we will also cherrypick this commit on tensorflow tensorflow tensorflow and tensorflow as these are also affected and still in supported range publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tensorflow tensorflow cpu tensorflow gpu check this box to open an automated fix pr isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree tensorflow isminimumfixversionavailable true minimumfixversion tensorflow tensorflow cpu tensorflow gpu basebranches vulnerabilityidentifier cve vulnerabilitydetails tensorflow is an end to end open source platform for machine learning an attacker can trigger a null pointer dereference by providing an invalid permutation to tf raw ops sparsematrixsparsecholesky this is because the implementation fails to properly validate the input arguments although validateinputs is called and there are checks in the body of this function the code proceeds to the next line in validateinputs since op requires is a macro that only exits the current function thus the first validation condition that fails in validateinputs will cause an early return from that function however the caller will continue execution from the next line the fix is to either explicitly check context or to convert validateinputs to return a status the fix will be included in tensorflow we will also cherrypick this commit on tensorflow tensorflow tensorflow and tensorflow as these are also affected and still in supported range vulnerabilityurl | 0 |
429,987 | 30,111,156,434 | IssuesEvent | 2023-06-30 07:52:36 | Nalini1998/Project_Public | https://api.github.com/repos/Nalini1998/Project_Public | opened | 7. Specify in the .inRange() method implement | documentation enhancement help wanted good first issue question | **Specify**: The next number method we will implement is .`inRange()`. Read the explanation and examples of the method in the linked documentation to get a sense of how the method should work.
Here is a summary of the method:
- .`inRange()` takes three arguments: a `number`, a `start` value, and an `end` value.
- .`inRange()` checks to see if the provided `number` falls within the range specified by the `start` and `end` values.
- If the provided number is smaller than the start value, .`inRange()` will return `false`.
- If the provided number is larger than or equal to the end value, .`inRange()` will return `false`.
- If the provided number is within the start and end values, .`inRange()` will return `true`.
- If no `end` value is provided to the method, the `start` value will be `0` and the `end` value will be the provided `start` value.
- If the provided `start` value is larger than the provided `end` value, the two values should be swapped. | 1.0 | 7. Specify in the .inRange() method implement - **Specify**: The next number method we will implement is .`inRange()`. Read the explanation and examples of the method in the linked documentation to get a sense of how the method should work.
Here is a summary of the method:
- .`inRange()` takes three arguments: a `number`, a `start` value, and an `end` value.
- .`inRange()` checks to see if the provided `number` falls within the range specified by the `start` and `end` values.
- If the provided number is smaller than the start value, .`inRange()` will return `false`.
- If the provided number is larger than or equal to the end value, .`inRange()` will return `false`.
- If the provided number is within the start and end values, .`inRange()` will return `true`.
- If no `end` value is provided to the method, the `start` value will be `0` and the `end` value will be the provided `start` value.
- If the provided `start` value is larger than the provided `end` value, the two values should be swapped. | non_main | specify in the inrange method implement specify the next number method we will implement is inrange read the explanation and examples of the method in the linked documentation to get a sense of how the method should work here is a summary of the method inrange takes three arguments a number a start value and an end value inrange checks to see if the provided number falls within the range specified by the start and end values if the provided number is smaller than the start value inrange will return false if the provided number is larger than or equal to the end value inrange will return false if the provided number is within the start and end values inrange will return true if no end value is provided to the method the start value will be and the end value will be the provided start value if the provided start value is larger than the provided end value the two values should be swapped | 0 |
687,719 | 23,536,525,892 | IssuesEvent | 2022-08-19 21:36:22 | lowRISC/opentitan | https://api.github.com/repos/lowRISC/opentitan | closed | [pinmux] D3 review opens | Priority:P2 Type:Task IP:pinmux Milestone:D3 | - [x] Cindy to look at [#3158](https://github.com/lowRISC/opentitan/issues/3158) and check whether it can be closed.
- [x] Waive USB submodule review and cover it as part of the USB checklist. https://github.com/lowRISC/opentitan/pull/14377
- [x] stick in a comment into RTL to explain the constant offset in the wakeup signal selection mux. https://github.com/lowRISC/opentitan/pull/14377 | 1.0 | [pinmux] D3 review opens - - [x] Cindy to look at [#3158](https://github.com/lowRISC/opentitan/issues/3158) and check whether it can be closed.
- [x] Waive USB submodule review and cover it as part of the USB checklist. https://github.com/lowRISC/opentitan/pull/14377
- [x] stick in a comment into RTL to explain the constant offset in the wakeup signal selection mux. https://github.com/lowRISC/opentitan/pull/14377 | non_main | review opens cindy to look at and check whether it can be closed waive usb submodule review and cover it as part of the usb checklist stick in a comment into rtl to explain the constant offset in the wakeup signal selection mux | 0 |
58,026 | 8,223,637,982 | IssuesEvent | 2018-09-06 11:16:53 | PowerShell/SqlServerDsc | https://api.github.com/repos/PowerShell/SqlServerDsc | closed | MSFT_SqlAGReplica failed to execute Set-TargetResource functionality with error message: HADR is not enabled | documentation good first issue help wanted | SqlServerLogin AddNTServiceClusSvc
{
Ensure = 'Present'
Name = 'NT SERVICE\ClusSvc'
LoginType = 'WindowsUser'
ServerName = $SqlNode
InstanceName = "MSSQLSERVER"
PsDscRunAsCredential = $SqlInstallCredential
}
# Add the required permissions to the cluster service login
SqlServerPermission AddNTServiceClusSvcPermissions
{
DependsOn = '[SqlServerLogin]AddNTServiceClusSvc'
Ensure = 'Present'
ServerName = $SqlNode
InstanceName = "MSSQLSERVER"
Principal = 'NT SERVICE\ClusSvc'
Permission = 'AlterAnyAvailabilityGroup', 'ViewServerState'
PsDscRunAsCredential = $SqlInstallCredential
}
SqlServerEndpoint HADREndpoint
{
EndPointName = 'HADR'
Ensure = 'Present'
Port = $portNumber
ServerName = $SqlNode
InstanceName = "MSSQLSERVER"
PsDscRunAsCredential = $SqlInstallCredential
}
SqlAGReplica AddReplica
{
Ensure = 'Present'
Name = $SqlNode
AvailabilityGroupName = $avgGroupName
ServerName = $SqlNode
InstanceName = "MSSQLSERVER"
PrimaryReplicaServerName = $SqlPrimaryReplicaNode
PrimaryReplicaInstanceName = "MSSQLSERVER"
PsDscRunAsCredential = $SqlInstallCredential
DependsOn = '[SqlSetup]InstallDefaultInstance'
} | 1.0 | MSFT_SqlAGReplica failed to execute Set-TargetResource functionality with error message: HADR is not enabled - SqlServerLogin AddNTServiceClusSvc
{
Ensure = 'Present'
Name = 'NT SERVICE\ClusSvc'
LoginType = 'WindowsUser'
ServerName = $SqlNode
InstanceName = "MSSQLSERVER"
PsDscRunAsCredential = $SqlInstallCredential
}
# Add the required permissions to the cluster service login
SqlServerPermission AddNTServiceClusSvcPermissions
{
DependsOn = '[SqlServerLogin]AddNTServiceClusSvc'
Ensure = 'Present'
ServerName = $SqlNode
InstanceName = "MSSQLSERVER"
Principal = 'NT SERVICE\ClusSvc'
Permission = 'AlterAnyAvailabilityGroup', 'ViewServerState'
PsDscRunAsCredential = $SqlInstallCredential
}
SqlServerEndpoint HADREndpoint
{
EndPointName = 'HADR'
Ensure = 'Present'
Port = $portNumber
ServerName = $SqlNode
InstanceName = "MSSQLSERVER"
PsDscRunAsCredential = $SqlInstallCredential
}
SqlAGReplica AddReplica
{
Ensure = 'Present'
Name = $SqlNode
AvailabilityGroupName = $avgGroupName
ServerName = $SqlNode
InstanceName = "MSSQLSERVER"
PrimaryReplicaServerName = $SqlPrimaryReplicaNode
PrimaryReplicaInstanceName = "MSSQLSERVER"
PsDscRunAsCredential = $SqlInstallCredential
DependsOn = '[SqlSetup]InstallDefaultInstance'
} | non_main | msft sqlagreplica failed to execute set targetresource functionality with error message hadr is not enabled sqlserverlogin addntserviceclussvc ensure present name nt service clussvc logintype windowsuser servername sqlnode instancename mssqlserver psdscrunascredential sqlinstallcredential add the required permissions to the cluster service login sqlserverpermission addntserviceclussvcpermissions dependson addntserviceclussvc ensure present servername sqlnode instancename mssqlserver principal nt service clussvc permission alteranyavailabilitygroup viewserverstate psdscrunascredential sqlinstallcredential sqlserverendpoint hadrendpoint endpointname hadr ensure present port portnumber servername sqlnode instancename mssqlserver psdscrunascredential sqlinstallcredential sqlagreplica addreplica ensure present name sqlnode availabilitygroupname avggroupname servername sqlnode instancename mssqlserver primaryreplicaservername sqlprimaryreplicanode primaryreplicainstancename mssqlserver psdscrunascredential sqlinstallcredential dependson installdefaultinstance | 0 |
102,050 | 11,273,095,228 | IssuesEvent | 2020-01-14 15:58:18 | rucio/rucio | https://api.github.com/repos/rucio/rucio | closed | Repository cleanup | Documentation Infrastructure Release management enhancement | Motivation
----------
There is quite a lot of unused files in the repository. We should clean this up:
- [x] `bin/` Should be fine
- [x] `doc/`
- `atlasnote/` remove
- `design/` remove
- [x] `etc/`
- [x] Some cleanup in the folder... `netmodel`... ?
- [x] `auditor` needed?
- [x] `docker`
- only keep demo and dev
- [x] `schemas` json schemas - need to check if use
- [x] `supervisord` remove or move to tools repo
- [x] `web`
- [x] ldap.cfg.template - This should be moved to a tools repo once we have it
- [x] `lib/` ok
- [x] `tools/`
- [x] hadoop - remove
- [x] patches/nose - remove
- [x] space-usage ?
- [x] travis - need
- [x] `tox.ini` can go | 1.0 | Repository cleanup - Motivation
----------
There is quite a lot of unused files in the repository. We should clean this up:
- [x] `bin/` Should be fine
- [x] `doc/`
- `atlasnote/` remove
- `design/` remove
- [x] `etc/`
- [x] Some cleanup in the folder... `netmodel`... ?
- [x] `auditor` needed?
- [x] `docker`
- only keep demo and dev
- [x] `schemas` json schemas - need to check if use
- [x] `supervisord` remove or move to tools repo
- [x] `web`
- [x] ldap.cfg.template - This should be moved to a tools repo once we have it
- [x] `lib/` ok
- [x] `tools/`
- [x] hadoop - remove
- [x] patches/nose - remove
- [x] space-usage ?
- [x] travis - need
- [x] `tox.ini` can go | non_main | repository cleanup motivation there is quite a lot of unused files in the repository we should clean this up bin should be fine doc atlasnote remove design remove etc some cleanup in the folder netmodel auditor needed docker only keep demo and dev schemas json schemas need to check if use supervisord remove or move to tools repo web ldap cfg template this should be moved to a tools repo once we have it lib ok tools hadoop remove patches nose remove space usage travis need tox ini can go | 0 |
15,897 | 20,102,575,482 | IssuesEvent | 2022-02-07 06:57:32 | SAP/openui5-docs | https://api.github.com/repos/SAP/openui5-docs | closed | Missing Deprecation Info for sap.ui.layout.form.GridLayout | In Process | `GridLayout` is listed as layout option for the `SimpleFormLayout` without any note about its deprecation:
https://openui5.hana.ondemand.com/api/sap.ui.layout.form.SimpleFormLayout | 1.0 | Missing Deprecation Info for sap.ui.layout.form.GridLayout - `GridLayout` is listed as layout option for the `SimpleFormLayout` without any note about its deprecation:
https://openui5.hana.ondemand.com/api/sap.ui.layout.form.SimpleFormLayout | non_main | missing deprecation info for sap ui layout form gridlayout gridlayout is listed as layout option for the simpleformlayout without any note about its deprecation | 0 |
83,076 | 23,960,600,643 | IssuesEvent | 2022-09-12 18:43:56 | lowRISC/opentitan | https://api.github.com/repos/lowRISC/opentitan | opened | [opentitantool] Consider adding the CRC check back to update-usr-access command | Component:Software Priority:P3 Type:Task SW:opentitantool SW:Build System | #14877 adds the `update-usr-access` to `opentitantool` and uses it in `bitstream_splice` to improve local workflows that involve splicing a locally built `rom` or `test_rom` into a bitstream from the GCS bucket. See #14865 for details.
One particular shortcoming of the implementation in #14877 is that it disables the CRC check during FPGA programming. We should consider enabling it again. | 1.0 | [opentitantool] Consider adding the CRC check back to update-usr-access command - #14877 adds the `update-usr-access` to `opentitantool` and uses it in `bitstream_splice` to improve local workflows that involve splicing a locally built `rom` or `test_rom` into a bitstream from the GCS bucket. See #14865 for details.
One particular shortcoming of the implementation in #14877 is that it disables the CRC check during FPGA programming. We should consider enabling it again. | non_main | consider adding the crc check back to update usr access command adds the update usr access to opentitantool and uses it in bitstream splice to improve local workflows that involve splicing a locally built rom or test rom into a bitstream from the gcs bucket see for details one particular shortcoming of the implementation in is that it disables the crc check during fpga programming we should consider enabling it again | 0 |
59,681 | 14,629,784,062 | IssuesEvent | 2020-12-23 16:27:31 | ballerina-platform/ballerina-standard-library | https://api.github.com/repos/ballerina-platform/ballerina-standard-library | opened | Dependabot PRs aren't Distinguishable | area/build | Currently the Standard Library Dependabot PRs are not distinguishable from the other PRs by looking at the title. The PR title should be changed to `[Dependabot] ___`.
@TharindaDilshan | 1.0 | Dependabot PRs aren't Distinguishable - Currently the Standard Library Dependabot PRs are not distinguishable from the other PRs by looking at the title. The PR title should be changed to `[Dependabot] ___`.
@TharindaDilshan | non_main | dependabot prs aren t distinguishable currently the standard library dependabot prs are not distinguishable from the other prs by looking at the title the pr title should be changed to tharindadilshan | 0 |
532,181 | 15,531,079,026 | IssuesEvent | 2021-03-13 21:50:23 | Psychoanalytic-Electronic-Publishing/PEP-Web-User-Interface | https://api.github.com/repos/Psychoanalytic-Electronic-Publishing/PEP-Web-User-Interface | closed | Feedback fails | High Priority bug | Was testing feedback, tried twice, after re-logging in the second time. Same result:
Error (for some reason, Github won't let me upload image/screenshot)
| 1.0 | Feedback fails - Was testing feedback, tried twice, after re-logging in the second time. Same result:
Error (for some reason, Github won't let me upload image/screenshot)
| non_main | feedback fails was testing feedback tried twice after re logging in the second time same result error for some reason github won t let me upload image screenshot | 0 |
17,607 | 4,174,961,541 | IssuesEvent | 2016-06-21 15:29:06 | telerik/kendo-ui-core | https://api.github.com/repos/telerik/kendo-ui-core | opened | Document limited touch gesture support when multiple Grid features rely on it | Documentation | 1043467 (Drawer + virtual Grid) | 1.0 | Document limited touch gesture support when multiple Grid features rely on it - 1043467 (Drawer + virtual Grid) | non_main | document limited touch gesture support when multiple grid features rely on it drawer virtual grid | 0 |
4,816 | 24,794,981,884 | IssuesEvent | 2022-10-24 16:27:54 | aws/serverless-application-model | https://api.github.com/repos/aws/serverless-application-model | closed | Feature request: Documentation update showing how to use ReportBatchItemFailures with SQS | area/docs maintainer/need-followup | Hello,
Can we get an update to the documentation located here: https://docs.aws.amazon.com/serverless-application-model/latest/developerguide/sam-property-function-sqs.html
that shows how someone could enable `FunctionResponseTypes` (also known as partial batch failure reporting)?
It technically works (example below):
```
Events:
SQSEvent:
Type: SQS
Properties:
Enabled: true
FunctionResponseTypes:
- ReportBatchItemFailures
Queue: !GetAtt MySqsQueue.Arn
BatchSize: 10
```
but just isn't documented.
If by chance (not necessary for this one) an example could be written in Python and provided on this documentation link: https://docs.aws.amazon.com/lambda/latest/dg/with-sqs.html#sqs-batchfailurereporting-syntax
That would be really great as well! The reason why for this Python example is because our documentation for DynamoDB + Kinesis ( https://docs.aws.amazon.com/lambda/latest/dg/with-ddb.html#streams-batchfailurereporting-bisect and https://docs.aws.amazon.com/lambda/latest/dg/with-kinesis.html#streams-batchfailurereporting-bisect) have examples in Java and Python, so it'd be good if our SQS documentation had parity: | True | Feature request: Documentation update showing how to use ReportBatchItemFailures with SQS - Hello,
Can we get an update to the documentation located here: https://docs.aws.amazon.com/serverless-application-model/latest/developerguide/sam-property-function-sqs.html
that shows how someone could enable `FunctionResponseTypes` (also known as partial batch failure reporting)?
It technically works (example below):
```
Events:
SQSEvent:
Type: SQS
Properties:
Enabled: true
FunctionResponseTypes:
- ReportBatchItemFailures
Queue: !GetAtt MySqsQueue.Arn
BatchSize: 10
```
but just isn't documented.
If by chance (not necessary for this one) an example could be written in Python and provided on this documentation link: https://docs.aws.amazon.com/lambda/latest/dg/with-sqs.html#sqs-batchfailurereporting-syntax
That would be really great as well! The reason why for this Python example is because our documentation for DynamoDB + Kinesis ( https://docs.aws.amazon.com/lambda/latest/dg/with-ddb.html#streams-batchfailurereporting-bisect and https://docs.aws.amazon.com/lambda/latest/dg/with-kinesis.html#streams-batchfailurereporting-bisect) have examples in Java and Python, so it'd be good if our SQS documentation had parity: | main | feature request documentation update showing how to use reportbatchitemfailures with sqs hello can we get an update to the documentation located here that shows how someone could enable functionresponsetypes also known as partial batch failure reporting it technically works example below events sqsevent type sqs properties enabled true functionresponsetypes reportbatchitemfailures queue getatt mysqsqueue arn batchsize but just isn t documented if by chance not necessary for this one an example could be written in python and provided on this documentation link that would be really great as well the reason why for this python example is because our documentation for dynamodb kinesis and have examples in java and python so it d be good if our sqs documentation had parity | 1 |
1,862 | 6,577,413,684 | IssuesEvent | 2017-09-12 00:44:30 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | "service: enable=yes/no" with spanish CentOS6 servers is broken | affects_2.0 bug_report docs_report waiting_on_maintainer | ##### ISSUE TYPE
- Documentation Report
##### COMPONENT NAME
service core module
##### ANSIBLE VERSION
```
ansible 2.0.1.0
(but I wouldn't discard other versions)
```
##### OS / ENVIRONMENT
CentOS 6.7
(at least)
##### SUMMARY
On CentOS6 at least, a spanish translator did a bad translating in some error messages returned to the command line by the chkconfig tool which break the "service enable=yes / no" option in Ansible.
It 's not a direct Ansible issue but Ansible is affected.
##### STEPS TO REPRODUCE
```
- name: Start myservice and enable it
service: name=myservice state=started enabled=yes
```
##### EXPECTED RESULTS
```
TASK [role : Start myservice and enable it ] ***********************************************
ok: [myservice]
```
##### ACTUAL RESULTS
<!--- What actually happened? If possible run with high verbosity (-vvvv) -->
```
TASK [role : Start myservice and enable it ] ***********************************************
fatal: [myservice]: FAILED! => {"changed": false, "failed": true, "msg": "service myservice does not support chkconfig"}
```
##### WHY
Line https://github.com/ansible/ansible-modules-core/blob/devel/system/service.py#L702 waits a concrete answer to do the regexp but, in Spanish, that line is bad translated changing the "--add" statement to "--añada" (doesn't make sense), so you see something like:
"El servicio myservice soporta chkconfig, pero no está registrado (ejecute \n'chkconfig -- añada myservice')\n"
the sentence "chkconfig --add" doesn't appear there and that breaks the "if". So the "enable" feature is broken.
##### WORKAROUND
`export LANG="en"`
in the terminal, before starting to work with any sofware which uses Ansible inside.
| True | "service: enable=yes/no" with spanish CentOS6 servers is broken - ##### ISSUE TYPE
- Documentation Report
##### COMPONENT NAME
service core module
##### ANSIBLE VERSION
```
ansible 2.0.1.0
(but I wouldn't discard other versions)
```
##### OS / ENVIRONMENT
CentOS 6.7
(at least)
##### SUMMARY
On CentOS6 at least, a spanish translator did a bad translating in some error messages returned to the command line by the chkconfig tool which break the "service enable=yes / no" option in Ansible.
It 's not a direct Ansible issue but Ansible is affected.
##### STEPS TO REPRODUCE
```
- name: Start myservice and enable it
service: name=myservice state=started enabled=yes
```
##### EXPECTED RESULTS
```
TASK [role : Start myservice and enable it ] ***********************************************
ok: [myservice]
```
##### ACTUAL RESULTS
<!--- What actually happened? If possible run with high verbosity (-vvvv) -->
```
TASK [role : Start myservice and enable it ] ***********************************************
fatal: [myservice]: FAILED! => {"changed": false, "failed": true, "msg": "service myservice does not support chkconfig"}
```
##### WHY
Line https://github.com/ansible/ansible-modules-core/blob/devel/system/service.py#L702 waits a concrete answer to do the regexp but, in Spanish, that line is bad translated changing the "--add" statement to "--añada" (doesn't make sense), so you see something like:
"El servicio myservice soporta chkconfig, pero no está registrado (ejecute \n'chkconfig -- añada myservice')\n"
the sentence "chkconfig --add" doesn't appear there and that breaks the "if". So the "enable" feature is broken.
##### WORKAROUND
`export LANG="en"`
in the terminal, before starting to work with any sofware which uses Ansible inside.
| main | service enable yes no with spanish servers is broken issue type documentation report component name service core module ansible version ansible but i wouldn t discard other versions os environment centos at least summary on at least a spanish translator did a bad translating in some error messages returned to the command line by the chkconfig tool which break the service enable yes no option in ansible it s not a direct ansible issue but ansible is affected steps to reproduce name start myservice and enable it service name myservice state started enabled yes expected results task ok actual results task fatal failed changed false failed true msg service myservice does not support chkconfig why line waits a concrete answer to do the regexp but in spanish that line is bad translated changing the add statement to añada doesn t make sense so you see something like el servicio myservice soporta chkconfig pero no está registrado ejecute n chkconfig añada myservice n the sentence chkconfig add doesn t appear there and that breaks the if so the enable feature is broken workaround export lang en in the terminal before starting to work with any sofware which uses ansible inside | 1 |
607 | 4,104,360,628 | IssuesEvent | 2016-06-05 09:59:06 | caskroom/homebrew-cask | https://api.github.com/repos/caskroom/homebrew-cask | closed | question: how to test a cask binary? | awaiting maintainer feedback | Various casks provide `binary` stanzas to symlink some binary or script within a cask-installed app.
Would it be possible or desirable to provide some lightweight functionality to automatically test that the `binary` actually results in a working command?
For example, the `praat` cask creates a symlink
```
/usr/local/bin/praat -> /opt/homebrew-cask/Caskroom/praat/#{installed_version}/Praat.app/Contents/MacOS/Praat
```
It would be nice to automatically check when the cask is tested or installed that running `praat` actually does run that `.../Praat.app/Contents/MacOS/Praat` binary.
Because sometimes paths inside apps are changed upstream, and the symlinks would break on installing an updated cask. Or some other stuff happens upstream, and the binary itself no longer works.
Catching this sort of issue during the test builds, and guarding against it during `postflight` might be a good idea. | True | question: how to test a cask binary? - Various casks provide `binary` stanzas to symlink some binary or script within a cask-installed app.
Would it be possible or desirable to provide some lightweight functionality to automatically test that the `binary` actually results in a working command?
For example, the `praat` cask creates a symlink
```
/usr/local/bin/praat -> /opt/homebrew-cask/Caskroom/praat/#{installed_version}/Praat.app/Contents/MacOS/Praat
```
It would be nice to automatically check when the cask is tested or installed that running `praat` actually does run that `.../Praat.app/Contents/MacOS/Praat` binary.
Because sometimes paths inside apps are changed upstream, and the symlinks would break on installing an updated cask. Or some other stuff happens upstream, and the binary itself no longer works.
Catching this sort of issue during the test builds, and guarding against it during `postflight` might be a good idea. | main | question how to test a cask binary various casks provide binary stanzas to symlink some binary or script within a cask installed app would it be possible or desirable to provide some lightweight functionality to automatically test that the binary actually results in a working command for example the praat cask creates a symlink usr local bin praat opt homebrew cask caskroom praat installed version praat app contents macos praat it would be nice to automatically check when the cask is tested or installed that running praat actually does run that praat app contents macos praat binary because sometimes paths inside apps are changed upstream and the symlinks would break on installing an updated cask or some other stuff happens upstream and the binary itself no longer works catching this sort of issue during the test builds and guarding against it during postflight might be a good idea | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.