Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 957 | labels stringlengths 4 795 | body stringlengths 1 259k | index stringclasses 12
values | text_combine stringlengths 96 259k | label stringclasses 2
values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
177,329 | 14,623,357,076 | IssuesEvent | 2020-12-23 03:07:00 | WSU-CASAS/AL | https://api.github.com/repos/WSU-CASAS/AL | opened | Don't generate statistical features for GPS sensors by default | documentation enhancement | We would not like to include the statistical features (mean, zero crossing, etc) for GPS sensors, as they do not provide much useful information (due to different peoples' GPS locations being different). Thus we would like to by default disable creating these features for GPS, with a flag to enable it in config if desi... | 1.0 | Don't generate statistical features for GPS sensors by default - We would not like to include the statistical features (mean, zero crossing, etc) for GPS sensors, as they do not provide much useful information (due to different peoples' GPS locations being different). Thus we would like to by default disable creating t... | non_priority | don t generate statistical features for gps sensors by default we would not like to include the statistical features mean zero crossing etc for gps sensors as they do not provide much useful information due to different peoples gps locations being different thus we would like to by default disable creating t... | 0 |
36,956 | 12,452,543,812 | IssuesEvent | 2020-05-27 12:28:54 | diennea/carapaceproxy | https://api.github.com/repos/diennea/carapaceproxy | closed | Carapace> possibility to change default pwd used by carapace to comunicate with the DB | Security enhancement | Currently, is not possible to change the default pwd used by Carapace for auth with the database.
So, if we change the db default pwd, Carapace will be not able to connect to database.
For security reason, i think is appropriate add posibility to set a custom pwd.
| True | Carapace> possibility to change default pwd used by carapace to comunicate with the DB - Currently, is not possible to change the default pwd used by Carapace for auth with the database.
So, if we change the db default pwd, Carapace will be not able to connect to database.
For security reason, i think is appropriat... | non_priority | carapace possibility to change default pwd used by carapace to comunicate with the db currently is not possible to change the default pwd used by carapace for auth with the database so if we change the db default pwd carapace will be not able to connect to database for security reason i think is appropriat... | 0 |
82,600 | 10,299,939,782 | IssuesEvent | 2019-08-28 11:47:22 | coderplex/donation-page | https://api.github.com/repos/coderplex/donation-page | closed | Add contribution.md file | documentation enhancement | - Specify how to run this project on local machine.
- Add contribution guidelines. | 1.0 | Add contribution.md file - - Specify how to run this project on local machine.
- Add contribution guidelines. | non_priority | add contribution md file specify how to run this project on local machine add contribution guidelines | 0 |
165,445 | 20,574,680,208 | IssuesEvent | 2022-03-04 02:23:38 | AlexRogalskiy/github-action-user-contribution | https://api.github.com/repos/AlexRogalskiy/github-action-user-contribution | closed | CVE-2022-0235 (Medium) detected in multiple libraries - autoclosed | security vulnerability | ## CVE-2022-0235 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-fetch-3.0.0-beta.9.tgz</b>, <b>node-fetch-2.6.6.tgz</b>, <b>node-fetch-2.6.1.tgz</b></p></summary>
<p>
<detail... | True | CVE-2022-0235 (Medium) detected in multiple libraries - autoclosed - ## CVE-2022-0235 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-fetch-3.0.0-beta.9.tgz</b>, <b>node-fetch-... | non_priority | cve medium detected in multiple libraries autoclosed cve medium severity vulnerability vulnerable libraries node fetch beta tgz node fetch tgz node fetch tgz node fetch beta tgz a light weight module that brings fetch api to node js library hom... | 0 |
269,953 | 20,513,167,548 | IssuesEvent | 2022-03-01 09:04:35 | ssciwr/adaptivefiltering | https://api.github.com/repos/ssciwr/adaptivefiltering | opened | Import adaptivefiltering as af in example notebooks | documentation enhancement | The name `adaptivefiltering` is quite long. We should use the following in all examples:
```
import adaptivefiltering as af
ds = af.DataSet(...)
```
Will make it much more readable. | 1.0 | Import adaptivefiltering as af in example notebooks - The name `adaptivefiltering` is quite long. We should use the following in all examples:
```
import adaptivefiltering as af
ds = af.DataSet(...)
```
Will make it much more readable. | non_priority | import adaptivefiltering as af in example notebooks the name adaptivefiltering is quite long we should use the following in all examples import adaptivefiltering as af ds af dataset will make it much more readable | 0 |
40,792 | 16,546,017,196 | IssuesEvent | 2021-05-28 00:10:21 | microsoft/vscode-cpptools | https://api.github.com/repos/microsoft/vscode-cpptools | closed | Designated struct initializtion with default values gives an error | Language Service Visual Studio bug fixed (release pending) | **Type: LanguageService**
When working on an OpenGL wrapper I stumbled upon what seems to be either a bug in IntelliSense or a as of yet not implemented feature. When trying to use designated initializers for a struct, it would not work when the struct had default values. The code compiled happily, but IntelliSense ... | 1.0 | Designated struct initializtion with default values gives an error - **Type: LanguageService**
When working on an OpenGL wrapper I stumbled upon what seems to be either a bug in IntelliSense or a as of yet not implemented feature. When trying to use designated initializers for a struct, it would not work when the st... | non_priority | designated struct initializtion with default values gives an error type languageservice when working on an opengl wrapper i stumbled upon what seems to be either a bug in intellisense or a as of yet not implemented feature when trying to use designated initializers for a struct it would not work when the st... | 0 |
61,986 | 7,540,926,119 | IssuesEvent | 2018-04-17 08:15:05 | owncloud/core | https://api.github.com/repos/owncloud/core | reopened | [9.0.3] [Accessibility] Feedback & Suggestions | design | One of our users analyzed our ownCloud instance for accessibility and we would be glad to share their conclusions with you.
> We are currently working to address the problems that can be fixed by changes in the theming. However, we would appreciate it if you could also work on improving the experience for challenged p... | 1.0 | [9.0.3] [Accessibility] Feedback & Suggestions - One of our users analyzed our ownCloud instance for accessibility and we would be glad to share their conclusions with you.
> We are currently working to address the problems that can be fixed by changes in the theming. However, we would appreciate it if you could also ... | non_priority | feedback suggestions one of our users analyzed our owncloud instance for accessibility and we would be glad to share their conclusions with you we are currently working to address the problems that can be fixed by changes in the theming however we would appreciate it if you could also work on improving th... | 0 |
26,927 | 4,833,485,607 | IssuesEvent | 2016-11-08 11:09:14 | primefaces/primeng | https://api.github.com/repos/primefaces/primeng | closed | Calendar 'onSelect' not fired on time change | defect | It seems that the `onSelect` event is not fired up if one only changes the **time** in a `p-calendar` with date and time. I didn't test with a time only calendar.
Is it possible to trigger it when time is also modified? | 1.0 | Calendar 'onSelect' not fired on time change - It seems that the `onSelect` event is not fired up if one only changes the **time** in a `p-calendar` with date and time. I didn't test with a time only calendar.
Is it possible to trigger it when time is also modified? | non_priority | calendar onselect not fired on time change it seems that the onselect event is not fired up if one only changes the time in a p calendar with date and time i didn t test with a time only calendar is it possible to trigger it when time is also modified | 0 |
80,247 | 10,166,452,476 | IssuesEvent | 2019-08-07 15:50:54 | hoobs-org/HOOBS | https://api.github.com/repos/hoobs-org/HOOBS | closed | Add readme - Credits | documentation | rocketsmarthome.com
HOOBS Hardware is Manufactured by rocketsmarthome.com
rocketsmarthome.com is the official Manufacturer of HOOBS in a Box and HOOBS on microSD.
Rocket Smart Home is an all-in-one home automation service provider with its own technology and certified installers.
The Smart Home solution for h... | 1.0 | Add readme - Credits - rocketsmarthome.com
HOOBS Hardware is Manufactured by rocketsmarthome.com
rocketsmarthome.com is the official Manufacturer of HOOBS in a Box and HOOBS on microSD.
Rocket Smart Home is an all-in-one home automation service provider with its own technology and certified installers.
The Sm... | non_priority | add readme credits rocketsmarthome com hoobs hardware is manufactured by rocketsmarthome com rocketsmarthome com is the official manufacturer of hoobs in a box and hoobs on microsd rocket smart home is an all in one home automation service provider with its own technology and certified installers the sm... | 0 |
138,473 | 18,793,935,998 | IssuesEvent | 2021-11-08 19:53:52 | Dima2022/hygieia-workflow-github-collector | https://api.github.com/repos/Dima2022/hygieia-workflow-github-collector | opened | CVE-2018-12023 (High) detected in jackson-databind-2.5.0.jar | security vulnerability | ## CVE-2018-12023 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.5.0.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2018-12023 (High) detected in jackson-databind-2.5.0.jar - ## CVE-2018-12023 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.5.0.jar</b></p></summary>
<p>General... | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file hygieia workflow github collect... | 0 |
8,752 | 12,289,692,371 | IssuesEvent | 2020-05-09 22:55:28 | topcoder-platform/challenge-engine-ui | https://api.github.com/repos/topcoder-platform/challenge-engine-ui | closed | Search > Search is not happening for single charecter | Functional May 7 Bug Hunt Not a requirement Rejected | **Describe the bug**
Search is not happening for single charecter.
**To Reproduce / Actual Behavior**
Steps to reproduce the behavior:
1. Go to https://challenges.topcoder-dev.com/
2. Click on Search text box
3. Enter only one charecter "x"
4. Press Enter in the keyboard
5. Search is not happening
**Expect... | 1.0 | Search > Search is not happening for single charecter - **Describe the bug**
Search is not happening for single charecter.
**To Reproduce / Actual Behavior**
Steps to reproduce the behavior:
1. Go to https://challenges.topcoder-dev.com/
2. Click on Search text box
3. Enter only one charecter "x"
4. Press Enter... | non_priority | search search is not happening for single charecter describe the bug search is not happening for single charecter to reproduce actual behavior steps to reproduce the behavior go to click on search text box enter only one charecter x press enter in the keyboard search is not ... | 0 |
112,968 | 24,347,009,921 | IssuesEvent | 2022-10-02 13:00:03 | AmreshSinha/Spotify-Cards-API | https://api.github.com/repos/AmreshSinha/Spotify-Cards-API | closed | Adding create card button option for user. | good first issue codepeak stale | **Is your feature request related to a problem? Please describe.**
Currently, there is no input or create card button option in the page. User has to copy the API link and hit the end points after entering the data in the url to get the result.
**Describe the solution you'd like**
A feature can be implemented fo... | 1.0 | Adding create card button option for user. - **Is your feature request related to a problem? Please describe.**
Currently, there is no input or create card button option in the page. User has to copy the API link and hit the end points after entering the data in the url to get the result.
**Describe the solution ... | non_priority | adding create card button option for user is your feature request related to a problem please describe currently there is no input or create card button option in the page user has to copy the api link and hit the end points after entering the data in the url to get the result describe the solution ... | 0 |
36,874 | 18,022,137,167 | IssuesEvent | 2021-09-16 20:56:37 | microsoft/AdaptiveCards | https://api.github.com/repos/microsoft/AdaptiveCards | closed | Consider templatizing access to JSON parser/producer | Area-Renderers Platform-Shared Model Request Area-Performance | Guys, as a C++ user I'm trying to adopt your object model (since I don't want to have to manually redo upcoming changes). In the process I feel I'm losing something by going from super-fast and good STL player rapidjson to your jsoncpp choice.
Since you've already isolated most usage of jsoncpp into the ParseUtils c... | True | Consider templatizing access to JSON parser/producer - Guys, as a C++ user I'm trying to adopt your object model (since I don't want to have to manually redo upcoming changes). In the process I feel I'm losing something by going from super-fast and good STL player rapidjson to your jsoncpp choice.
Since you've alrea... | non_priority | consider templatizing access to json parser producer guys as a c user i m trying to adopt your object model since i don t want to have to manually redo upcoming changes in the process i feel i m losing something by going from super fast and good stl player rapidjson to your jsoncpp choice since you ve alrea... | 0 |
67,139 | 7,036,509,611 | IssuesEvent | 2017-12-28 09:14:35 | kingalois/friedmanng | https://api.github.com/repos/kingalois/friedmanng | closed | Create test for GraveOwner | Alois testing | @flomue99 and @jonasmuehleder
I wrote a example for a test of class GarevOwner . For implementation see Class GraveOwnerTest | 1.0 | Create test for GraveOwner - @flomue99 and @jonasmuehleder
I wrote a example for a test of class GarevOwner . For implementation see Class GraveOwnerTest | non_priority | create test for graveowner and jonasmuehleder i wrote a example for a test of class garevowner for implementation see class graveownertest | 0 |
99,501 | 16,446,403,819 | IssuesEvent | 2021-05-20 20:09:47 | snowdensb/nibrs | https://api.github.com/repos/snowdensb/nibrs | opened | CVE-2020-10673 (High) detected in multiple libraries | security vulnerability | ## CVE-2020-10673 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.9.5.jar</b>, <b>jackson-databind-2.8.10.jar</b>, <b>jackson-databind-2.9.8.jar</b>, <b>jackson-dat... | True | CVE-2020-10673 (High) detected in multiple libraries - ## CVE-2020-10673 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.9.5.jar</b>, <b>jackson-databind-2.8.10.jar... | non_priority | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries jackson databind jar jackson databind jar jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackso... | 0 |
270,894 | 29,145,871,083 | IssuesEvent | 2023-05-18 02:48:38 | aayant-mend/WebGoat | https://api.github.com/repos/aayant-mend/WebGoat | opened | commons-io-2.6.jar: 1 vulnerabilities (highest severity is: 4.8) | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-io-2.6.jar</b></p></summary>
<p>The Apache Commons IO library contains utility classes, stream implementations, file filters,
file comparators, endian transfo... | True | commons-io-2.6.jar: 1 vulnerabilities (highest severity is: 4.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-io-2.6.jar</b></p></summary>
<p>The Apache Commons IO library contains utility classes, str... | non_priority | commons io jar vulnerabilities highest severity is vulnerable library commons io jar the apache commons io library contains utility classes stream implementations file filters file comparators endian transformation classes and much more library home page a href path to depe... | 0 |
64,320 | 18,431,727,008 | IssuesEvent | 2021-10-14 08:28:50 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | Password reset modal text is double-escaped. | T-Defect P2 S-Minor Z-Rageshake A-Password-Reset | Reset your password - the password reset email send confirmation message reads:
"An email has been sent to XXX@XXX. Once you've followed the link it contains, click below."
The text has been double escaped. | 1.0 | Password reset modal text is double-escaped. - Reset your password - the password reset email send confirmation message reads:
"An email has been sent to XXX@XXX. Once you've followed the link it contains, click below."
The text has been double escaped. | non_priority | password reset modal text is double escaped reset your password the password reset email send confirmation message reads an email has been sent to xxx xxx once you ve followed the link it contains click below the text has been double escaped | 0 |
328,633 | 24,193,088,704 | IssuesEvent | 2022-09-23 19:48:58 | nextgenhealthcare/connect | https://api.github.com/repos/nextgenhealthcare/connect | opened | com.mirth.connect.connectors.file.FileReceiver: Error polling in channel | documentation | I have the following problem with the Mirth Connect application, in which this channel has communication with an SSH server.
Do you know what exactly it refers to?
ERROR 2022-09-14 22:18:21,274 [Timer-1] com.mirth.connect.connectors.file.FileReceiver: Error polling in channel: 0c708f73-8567-454a-84ff-3d11bfd70cd4... | 1.0 | com.mirth.connect.connectors.file.FileReceiver: Error polling in channel - I have the following problem with the Mirth Connect application, in which this channel has communication with an SSH server.
Do you know what exactly it refers to?
ERROR 2022-09-14 22:18:21,274 [Timer-1] com.mirth.connect.connectors.file.F... | non_priority | com mirth connect connectors file filereceiver error polling in channel i have the following problem with the mirth connect application in which this channel has communication with an ssh server do you know what exactly it refers to error com mirth connect connectors file filereceiver error... | 0 |
21,951 | 11,660,542,783 | IssuesEvent | 2020-03-03 03:42:06 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | opened | VZV | Map | Overlays | Epic Need: 1-Must Have Product: Vision Zero Crash Data System Product: Vision Zero Viewer Project: Vision Zero Viewer Service: Dev Workgroup: VZ migrated | The overlays components in the map section of VZV allow users to see additional polygons and lines of special features. The four features that we will be allowing the user to enable are:
- High Injury Network
- Speed Limits
- Austin City Council Districts
- ASMP Street Level
Overlay rules:
- The user should only be a... | 1.0 | VZV | Map | Overlays - The overlays components in the map section of VZV allow users to see additional polygons and lines of special features. The four features that we will be allowing the user to enable are:
- High Injury Network
- Speed Limits
- Austin City Council Districts
- ASMP Street Level
Overlay rules:
- Th... | non_priority | vzv map overlays the overlays components in the map section of vzv allow users to see additional polygons and lines of special features the four features that we will be allowing the user to enable are high injury network speed limits austin city council districts asmp street level overlay rules th... | 0 |
681 | 2,564,467,070 | IssuesEvent | 2015-02-06 20:02:26 | nathan-rice/ctools | https://api.github.com/repos/nathan-rice/ctools | opened | Incorporate air infiltration model | Database Modification Dispersion code enhancement Medium | IE will provide new model code. This may involve reading additional inputs from an additional database, where census block level information is used to predict an average in-home exposure based on model ambient air concentrations. | 1.0 | Incorporate air infiltration model - IE will provide new model code. This may involve reading additional inputs from an additional database, where census block level information is used to predict an average in-home exposure based on model ambient air concentrations. | non_priority | incorporate air infiltration model ie will provide new model code this may involve reading additional inputs from an additional database where census block level information is used to predict an average in home exposure based on model ambient air concentrations | 0 |
44,138 | 9,544,238,007 | IssuesEvent | 2019-05-01 13:36:16 | bryangarner/GEOG575_Finalproject | https://api.github.com/repos/bryangarner/GEOG575_Finalproject | closed | Point Clustering | *Kevin* Code Web App | Look into point clustering options. See if it's something we want to implement.
Some links:
https://github.com/adammertel/Leaflet.MarkerCluster.PlacementStrategies
https://adammertel.github.io/Leaflet.MarkerCluster.PlacementStrategies/demo/demo1.html
https://github.com/jawj/OverlappingMarkerSpiderfier-Leaf... | 1.0 | Point Clustering - Look into point clustering options. See if it's something we want to implement.
Some links:
https://github.com/adammertel/Leaflet.MarkerCluster.PlacementStrategies
https://adammertel.github.io/Leaflet.MarkerCluster.PlacementStrategies/demo/demo1.html
https://github.com/jawj/OverlappingMa... | non_priority | point clustering look into point clustering options see if it s something we want to implement some links | 0 |
171,046 | 13,214,320,099 | IssuesEvent | 2020-08-16 17:10:01 | duplicati/duplicati | https://api.github.com/repos/duplicati/duplicati | closed | S3 backup whitespace error | needs testing | Running on linux with version 2.0.0.73_preview_2014-11-11.
Fairly regularly, a backup to S3 gives the following error during a backup:
Operation Put with file duplicati-xxxxxx.dblock.zip.aes attempt 1 of 5 failed with message: Whitespace is required between PUBLIC id and SYSTEM id. Line 1, position 63. => Whitespace ... | 1.0 | S3 backup whitespace error - Running on linux with version 2.0.0.73_preview_2014-11-11.
Fairly regularly, a backup to S3 gives the following error during a backup:
Operation Put with file duplicati-xxxxxx.dblock.zip.aes attempt 1 of 5 failed with message: Whitespace is required between PUBLIC id and SYSTEM id. Line 1... | non_priority | backup whitespace error running on linux with version preview fairly regularly a backup to gives the following error during a backup operation put with file duplicati xxxxxx dblock zip aes attempt of failed with message whitespace is required between public id and system id line positi... | 0 |
32,281 | 13,784,761,918 | IssuesEvent | 2020-10-08 21:26:48 | microsoft/vscode-cpptools | https://api.github.com/repos/microsoft/vscode-cpptools | closed | Add a command to filter out references by "type" | Feature Request Feature: Find All References Language Service Works in VS help wanted more votes needed | Currently all "types" of references are show in the "C/C++: References" output. It would be nice to have a command to filter out unwanted "types" -- however, from my experience, it seems like all the "types" are potentially useful to see...so let us know if you really don't be able to filter stuff out (or if anyone wan... | 1.0 | Add a command to filter out references by "type" - Currently all "types" of references are show in the "C/C++: References" output. It would be nice to have a command to filter out unwanted "types" -- however, from my experience, it seems like all the "types" are potentially useful to see...so let us know if you really ... | non_priority | add a command to filter out references by type currently all types of references are show in the c c references output it would be nice to have a command to filter out unwanted types however from my experience it seems like all the types are potentially useful to see so let us know if you really ... | 0 |
193,662 | 22,216,251,637 | IssuesEvent | 2022-06-08 02:11:13 | maddyCode23/linux-4.1.15 | https://api.github.com/repos/maddyCode23/linux-4.1.15 | reopened | CVE-2017-5551 (Medium) detected in linux-stable-rtv4.1.33 | security vulnerability | ## CVE-2017-5551 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home pa... | True | CVE-2017-5551 (Medium) detected in linux-stable-rtv4.1.33 - ## CVE-2017-5551 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Car... | non_priority | cve medium detected in linux stable cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source f... | 0 |
22,638 | 7,196,882,944 | IssuesEvent | 2018-02-05 06:18:55 | ShaikASK/Testing | https://api.github.com/repos/ShaikASK/Testing | closed | Workflow : drag and drop complete folder documents are missing | Build version#5 Defect P1 SumFive Team | Steps To Replicate ::
1.Launch the url :http://192.168.1.197:3000/#
2.Login as HR Admin user
3.Select 'Work Flows' menu
4. Navigate to 'Folders' menu and create a folder with few document
5. Navigate to Work flow menu
6.Click on add (+) symbol displayed adjacent to workflow
7.Click on Add Steps >> Drag complet... | 1.0 | Workflow : drag and drop complete folder documents are missing - Steps To Replicate ::
1.Launch the url :http://192.168.1.197:3000/#
2.Login as HR Admin user
3.Select 'Work Flows' menu
4. Navigate to 'Folders' menu and create a folder with few document
5. Navigate to Work flow menu
6.Click on add (+) symbol di... | non_priority | workflow drag and drop complete folder documents are missing steps to replicate launch the url login as hr admin user select work flows menu navigate to folders menu and create a folder with few document navigate to work flow menu click on add symbol displayed adjacent to workfl... | 0 |
73,552 | 9,670,203,481 | IssuesEvent | 2019-05-21 19:18:07 | hashicorp/terraform | https://api.github.com/repos/hashicorp/terraform | closed | TF_CLI_CONFIG_FILE not respected | documentation | <!--
Hi there,
Thank you for opening an issue. Please note that we try to keep the Terraform issue tracker reserved for bug reports and feature requests. For general usage questions, please see: https://www.terraform.io/community.html.
If your issue relates to a specific Terraform provider, please open it in the... | 1.0 | TF_CLI_CONFIG_FILE not respected - <!--
Hi there,
Thank you for opening an issue. Please note that we try to keep the Terraform issue tracker reserved for bug reports and feature requests. For general usage questions, please see: https://www.terraform.io/community.html.
If your issue relates to a specific Terraf... | non_priority | tf cli config file not respected hi there thank you for opening an issue please note that we try to keep the terraform issue tracker reserved for bug reports and feature requests for general usage questions please see if your issue relates to a specific terraform provider please open it in the pro... | 0 |
66,400 | 14,768,308,782 | IssuesEvent | 2021-01-10 11:26:19 | kadirselcuk/core | https://api.github.com/repos/kadirselcuk/core | opened | WS-2018-0084 (High) detected in sshpk-1.13.1.tgz | security vulnerability | ## WS-2018-0084 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sshpk-1.13.1.tgz</b></p></summary>
<p>A library for finding and using SSH public keys</p>
<p>Library home page: <a href=... | True | WS-2018-0084 (High) detected in sshpk-1.13.1.tgz - ## WS-2018-0084 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sshpk-1.13.1.tgz</b></p></summary>
<p>A library for finding and using... | non_priority | ws high detected in sshpk tgz ws high severity vulnerability vulnerable library sshpk tgz a library for finding and using ssh public keys library home page a href path to dependency file core turbo registry sync package json path to vulnerable library core turbo regi... | 0 |
32,188 | 26,519,033,121 | IssuesEvent | 2023-01-18 23:58:33 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | How to build CoreCLR on windows arm64ec using MSVC | question area-Infrastructure-coreclr | ### Description
We try MSVC to run `.\build.cmd -subset clr+libs -c release -arch x64` build on x64, it works. But we tried to build for target arm64ec and run `.\build.cmd -subset clr+libs -c release -arch ARM64EC`, display error:
```
F:\gitP\dotnet\runtime\eng\build.ps1 : Cannot validate argument on parameter 'a... | 1.0 | How to build CoreCLR on windows arm64ec using MSVC - ### Description
We try MSVC to run `.\build.cmd -subset clr+libs -c release -arch x64` build on x64, it works. But we tried to build for target arm64ec and run `.\build.cmd -subset clr+libs -c release -arch ARM64EC`, display error:
```
F:\gitP\dotnet\runtime\eng... | non_priority | how to build coreclr on windows using msvc description we try msvc to run build cmd subset clr libs c release arch build on it works but we tried to build for target and run build cmd subset clr libs c release arch display error f gitp dotnet runtime eng build cannot vali... | 0 |
251,948 | 21,528,981,683 | IssuesEvent | 2022-04-28 21:40:55 | damccorm/test-migration-target | https://api.github.com/repos/damccorm/test-migration-target | opened | PubsubTableProviderIT.testSQLSelectsArrayAttributes[0] failing in SQL PostCommit | bug test-failures P3 dsl-sql |
Failing since https://ci-beam.apache.org/job/beam_PostCommit_SQL/6260/
```
java.lang.AssertionError: Did not receive signal on projects/apache-beam-testing/subscriptions/result-subscription--1731534761628855545
in 60s
at org.apache.beam.sdk.io.gcp.pubsub.TestPubsubSignal.pollForResultForDuration(TestPubsubSigna... | 1.0 | PubsubTableProviderIT.testSQLSelectsArrayAttributes[0] failing in SQL PostCommit -
Failing since https://ci-beam.apache.org/job/beam_PostCommit_SQL/6260/
```
java.lang.AssertionError: Did not receive signal on projects/apache-beam-testing/subscriptions/result-subscription--1731534761628855545
in 60s
at org.apac... | non_priority | pubsubtableproviderit testsqlselectsarrayattributes failing in sql postcommit failing since java lang assertionerror did not receive signal on projects apache beam testing subscriptions result subscription in at org apache beam sdk io gcp pubsub testpubsubsignal pollforresultforduration testpubsu... | 0 |
12,973 | 9,818,511,209 | IssuesEvent | 2019-06-13 19:26:43 | Azure/azure-sdk-for-java | https://api.github.com/repos/Azure/azure-sdk-for-java | closed | Retrieving the Diagnostics Storage account for an Azure SQL Database | Question SQL Service Attention | Looking for a way to get the Storage account which stores the diagnostics data for an Azure SQL Database.
We have added a diagnostic setting to an Azure SQL Database to archive its metrics to a Storage account as shown below.
<img width="953" alt="screenshot 185" src="https://user-images.githubusercontent.com/288... | 1.0 | Retrieving the Diagnostics Storage account for an Azure SQL Database - Looking for a way to get the Storage account which stores the diagnostics data for an Azure SQL Database.
We have added a diagnostic setting to an Azure SQL Database to archive its metrics to a Storage account as shown below.
<img width="953" ... | non_priority | retrieving the diagnostics storage account for an azure sql database looking for a way to get the storage account which stores the diagnostics data for an azure sql database we have added a diagnostic setting to an azure sql database to archive its metrics to a storage account as shown below img width al... | 0 |
126,073 | 17,868,825,541 | IssuesEvent | 2021-09-06 12:57:16 | fasttrack-solutions/jQuery-QueryBuilder | https://api.github.com/repos/fasttrack-solutions/jQuery-QueryBuilder | opened | WS-2020-0163 (Medium) detected in marked-0.6.2.tgz | security vulnerability | ## WS-2020-0163 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.6.2.tgz</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://reg... | True | WS-2020-0163 (Medium) detected in marked-0.6.2.tgz - ## WS-2020-0163 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.6.2.tgz</b></p></summary>
<p>A markdown parser built for... | non_priority | ws medium detected in marked tgz ws medium severity vulnerability vulnerable library marked tgz a markdown parser built for speed library home page a href path to dependency file jquery querybuilder package json path to vulnerable library jquery querybuilder node mod... | 0 |
27,842 | 8,041,621,403 | IssuesEvent | 2018-07-31 04:06:44 | opencv/opencv | https://api.github.com/repos/opencv/opencv | closed | OpenCV 3.4.1 with CUDA 8.0.44 ld issue | category: build/install category: gpu (cuda) | <!--
If you have a question rather than reporting a bug please go to http://answers.opencv.org where you get much faster responses.
If you need further assistance please read [How To Contribute](https://github.com/opencv/opencv/wiki/How_to_contribute).
This is a template helping you to create an issue which can be... | 1.0 | OpenCV 3.4.1 with CUDA 8.0.44 ld issue - <!--
If you have a question rather than reporting a bug please go to http://answers.opencv.org where you get much faster responses.
If you need further assistance please read [How To Contribute](https://github.com/opencv/opencv/wiki/How_to_contribute).
This is a template he... | non_priority | opencv with cuda ld issue if you have a question rather than reporting a bug please go to where you get much faster responses if you need further assistance please read this is a template helping you to create an issue which can be processed as quickly as possible this is the bug reporti... | 0 |
2,580 | 2,747,244,530 | IssuesEvent | 2015-04-23 00:16:22 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | wrong creation-timestamp set when article-save2copy | No Code Attached Yet | #### Steps to reproduce the issue
Go into the article-manager
Edit an article
Make a new article by save as copy button. [save2copy - function]
Look to the article option (creation-date/-time, saving-date/-time)
You will find:
creation-date/-time is the **source date/time.** .... and that is wrong !!!!!!!!
... | 1.0 | wrong creation-timestamp set when article-save2copy - #### Steps to reproduce the issue
Go into the article-manager
Edit an article
Make a new article by save as copy button. [save2copy - function]
Look to the article option (creation-date/-time, saving-date/-time)
You will find:
creation-date/-time is the *... | non_priority | wrong creation timestamp set when article steps to reproduce the issue go into the article manager edit an article make a new article by save as copy button look to the article option creation date time saving date time you will find creation date time is the source date time an... | 0 |
281,573 | 21,315,416,575 | IssuesEvent | 2022-04-16 07:22:59 | Denniszedead/pe | https://api.github.com/repos/Denniszedead/pe | opened | Appendix: Instructions for manual testing in the DG not complete | type.DocumentationBug severity.Medium | 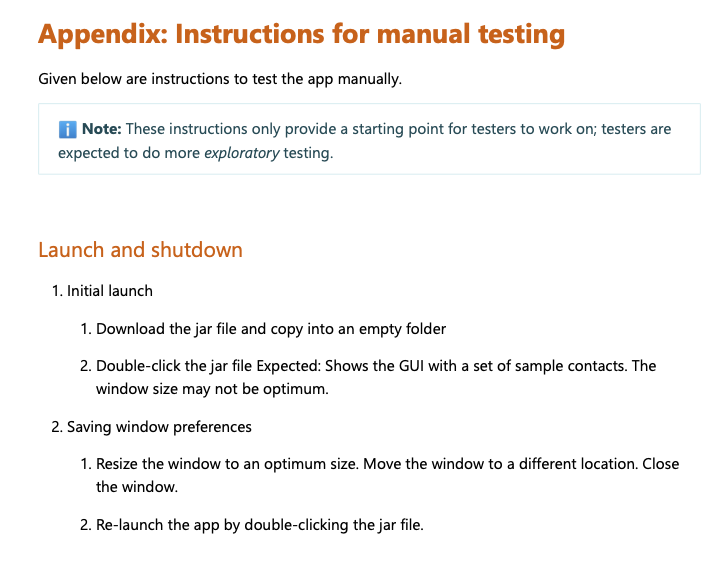
The appendix is not completed as all the commands as stated in the UG are not inside the appendix for the manual tester to stress test, especially when the testes test will ... | 1.0 | Appendix: Instructions for manual testing in the DG not complete - 
The appendix is not completed as all the commands as stated in the UG are not inside the appendix for the ... | non_priority | appendix instructions for manual testing in the dg not complete the appendix is not completed as all the commands as stated in the ug are not inside the appendix for the manual tester to stress test especially when the testes test will refer to this during pe | 0 |
197,632 | 15,686,881,342 | IssuesEvent | 2021-03-25 13:03:50 | r-lib/pkgdown | https://api.github.com/repos/r-lib/pkgdown | closed | Adding basic docs about styling? | documentation help wanted :heart: | (sorry if it's already there and I missed it!)
Docs along the line of the "basics of styling pkgdown" section of https://enpiar.com/2017/12/18/integrating-pkgdown-with-your-personal-website/ would be nice. :smile_cat: | 1.0 | Adding basic docs about styling? - (sorry if it's already there and I missed it!)
Docs along the line of the "basics of styling pkgdown" section of https://enpiar.com/2017/12/18/integrating-pkgdown-with-your-personal-website/ would be nice. :smile_cat: | non_priority | adding basic docs about styling sorry if it s already there and i missed it docs along the line of the basics of styling pkgdown section of would be nice smile cat | 0 |
33,235 | 7,681,141,937 | IssuesEvent | 2018-05-16 06:05:53 | ikigaidojo/cospace | https://api.github.com/repos/ikigaidojo/cospace | closed | Implement the association between an Admin and MembershipType | code implementation | - [ ] write an rspec test that confirms that association between the Admin and MembershipType. The test should cover both bidirectional association. | 1.0 | Implement the association between an Admin and MembershipType - - [ ] write an rspec test that confirms that association between the Admin and MembershipType. The test should cover both bidirectional association. | non_priority | implement the association between an admin and membershiptype write an rspec test that confirms that association between the admin and membershiptype the test should cover both bidirectional association | 0 |
70,295 | 13,447,613,929 | IssuesEvent | 2020-09-08 14:27:34 | e4exp/paper_manager_abstract | https://api.github.com/repos/e4exp/paper_manager_abstract | closed | Visual Compiler: Towards Translating Digital UI Design Draft to Front-End Code Automatically | 2020 Code Generation Pix2code UI Design _read_later | * https://link.springer.com/chapter/10.1007/978-3-030-50017-7_28
* HCII 2020: Human Interface and the Management of Information. Interacting with Information pp 385-394
フロントエンドエンジニアの仕事の一つに、UI(ユーザーインターフェース)設計案をプログラム互換性のあるアレンジに変換することがあります。
顧客の要求を満たすために、エンジニアは通常、画面サイズの幅が広いなど、さまざまな端末デバイスに対応するためのさまざまな要素を考慮する必要があります。
こ... | 2.0 | Visual Compiler: Towards Translating Digital UI Design Draft to Front-End Code Automatically - * https://link.springer.com/chapter/10.1007/978-3-030-50017-7_28
* HCII 2020: Human Interface and the Management of Information. Interacting with Information pp 385-394
フロントエンドエンジニアの仕事の一つに、UI(ユーザーインターフェース)設計案をプログラム互換性のあるア... | non_priority | visual compiler towards translating digital ui design draft to front end code automatically hcii human interface and the management of information interacting with information pp フロントエンドエンジニアの仕事の一つに、ui(ユーザーインターフェース)設計案をプログラム互換性のあるアレンジに変換することがあります。 顧客の要求を満たすために、エンジニアは通常、画面サイズの幅が広いなど、さまざまな端末デバイスに対応す... | 0 |
139,009 | 18,817,772,650 | IssuesEvent | 2021-11-10 02:38:02 | raindigi/reaction | https://api.github.com/repos/raindigi/reaction | opened | CVE-2021-3807 (High) detected in ansi-regex-3.0.0.tgz | security vulnerability | ## CVE-2021-3807 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ansi-regex-3.0.0.tgz</b></p></summary>
<p>Regular expression for matching ANSI escape codes</p>
<p>Library home page: <... | True | CVE-2021-3807 (High) detected in ansi-regex-3.0.0.tgz - ## CVE-2021-3807 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ansi-regex-3.0.0.tgz</b></p></summary>
<p>Regular expression fo... | non_priority | cve high detected in ansi regex tgz cve high severity vulnerability vulnerable library ansi regex tgz regular expression for matching ansi escape codes library home page a href path to dependency file reaction package json path to vulnerable library reaction node mod... | 0 |
222,670 | 24,711,236,899 | IssuesEvent | 2022-10-20 01:06:02 | rgordon95/advanced-react-demo | https://api.github.com/repos/rgordon95/advanced-react-demo | opened | CVE-2022-3517 (High) detected in minimatch-3.0.4.tgz | security vulnerability | ## CVE-2022-3517 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimatch-3.0.4.tgz</b></p></summary>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://regist... | True | CVE-2022-3517 (High) detected in minimatch-3.0.4.tgz - ## CVE-2022-3517 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimatch-3.0.4.tgz</b></p></summary>
<p>a glob matcher in javas... | non_priority | cve high detected in minimatch tgz cve high severity vulnerability vulnerable library minimatch tgz a glob matcher in javascript library home page a href path to dependency file advanced react demo package json path to vulnerable library node modules minimatch pack... | 0 |
8,776 | 11,899,692,648 | IssuesEvent | 2020-03-30 09:25:24 | prisma/prisma2 | https://api.github.com/repos/prisma/prisma2 | closed | Add `cli` as executable for @prisma/cli? | kind/improvement process/candidate topic: cli | ## Problem
When using npx without having `@prisma/cli` installed before we need to do `npx -p @prisma/cli@alpha prisma2 --version`
## Solution
If we put another name for the executable in the package.json `cli` npx should work like:
`npx @prisma/cli@alpha --version` which is a lot easier (no parameters!)
## A... | 1.0 | Add `cli` as executable for @prisma/cli? - ## Problem
When using npx without having `@prisma/cli` installed before we need to do `npx -p @prisma/cli@alpha prisma2 --version`
## Solution
If we put another name for the executable in the package.json `cli` npx should work like:
`npx @prisma/cli@alpha --version` whi... | non_priority | add cli as executable for prisma cli problem when using npx without having prisma cli installed before we need to do npx p prisma cli alpha version solution if we put another name for the executable in the package json cli npx should work like npx prisma cli alpha version which is ... | 0 |
318,717 | 23,736,951,147 | IssuesEvent | 2022-08-31 08:57:01 | blockscout/blockscout | https://api.github.com/repos/blockscout/blockscout | closed | Add the list of JSON RPC calls Blockscout makes to the node | documentation | Add *.md* document to the `./docs` folder with the list of JSON RPC calls Blockscout makes to Ethereum node | 1.0 | Add the list of JSON RPC calls Blockscout makes to the node - Add *.md* document to the `./docs` folder with the list of JSON RPC calls Blockscout makes to Ethereum node | non_priority | add the list of json rpc calls blockscout makes to the node add md document to the docs folder with the list of json rpc calls blockscout makes to ethereum node | 0 |
152,416 | 12,104,249,452 | IssuesEvent | 2020-04-20 19:52:01 | airween/crs | https://api.github.com/repos/airween/crs | opened | Second issue, with custom LABEL | TEST LABEL FOR MIGRATION | _Issue originally created by user fzipi on date 2020-03-10 14:23:38.
Link to original issue: https://github.com/crstest2/crs/issues/2._
We use a custom label here, to see if this will work. | 1.0 | Second issue, with custom LABEL - _Issue originally created by user fzipi on date 2020-03-10 14:23:38.
Link to original issue: https://github.com/crstest2/crs/issues/2._
We use a custom label here, to see if this will work. | non_priority | second issue with custom label issue originally created by user fzipi on date link to original issue we use a custom label here to see if this will work | 0 |
230,654 | 17,632,232,374 | IssuesEvent | 2021-08-19 09:24:31 | hashicorp/terraform-provider-azurerm | https://api.github.com/repos/hashicorp/terraform-provider-azurerm | closed | Documentation is not clear about azurerm provider definition for version 2.0.0 and features | enhancement question documentation | Hi, I spend few hours try to understand why a so simple code like the following was not working with the lastest azurerm provider :
```
variable "AzureRegion" {
type = string
}
variable "ResourceGroupName" {
type = string
}
# Azure Resource Group
resource "azurerm_resource_group" "Terra-RG-Sta... | 1.0 | Documentation is not clear about azurerm provider definition for version 2.0.0 and features - Hi, I spend few hours try to understand why a so simple code like the following was not working with the lastest azurerm provider :
```
variable "AzureRegion" {
type = string
}
variable "ResourceGroupName" {
... | non_priority | documentation is not clear about azurerm provider definition for version and features hi i spend few hours try to understand why a so simple code like the following was not working with the lastest azurerm provider variable azureregion type string variable resourcegroupname ... | 0 |
9,797 | 4,644,055,997 | IssuesEvent | 2016-09-30 15:16:03 | mitchellh/packer | https://api.github.com/repos/mitchellh/packer | closed | Error 2 when trying to compile | build-failure question | Here is what I am doing:
$ export GOPATH=`pwd`
$ go get -u github.com/mitchellh/gox
$ go get github.com/mitchellh/packer
$ cd $GOPATH/src/github.com/mitchellh/packer
$ make updatedeps
go get -u github.com/mitchellh/gox
go get -u golang.org/x/tools/cmd/stringer
INFO: Packer deps are managed by godep. See CONT... | 1.0 | Error 2 when trying to compile - Here is what I am doing:
$ export GOPATH=`pwd`
$ go get -u github.com/mitchellh/gox
$ go get github.com/mitchellh/packer
$ cd $GOPATH/src/github.com/mitchellh/packer
$ make updatedeps
go get -u github.com/mitchellh/gox
go get -u golang.org/x/tools/cmd/stringer
INFO: Packer de... | non_priority | error when trying to compile here is what i am doing export gopath pwd go get u github com mitchellh gox go get github com mitchellh packer cd gopath src github com mitchellh packer make updatedeps go get u github com mitchellh gox go get u golang org x tools cmd stringer info packer de... | 0 |
114,339 | 17,199,717,500 | IssuesEvent | 2021-07-17 01:40:53 | teamhephy/docker-base | https://api.github.com/repos/teamhephy/docker-base | closed | rethink "statically tagged" images | proposal security | _From @bacongobbler on September 23, 2016 9:0_
Our current tagging workflow for docker-base goes like this:
- PR a few new features
- tag it
- :shipit:
One use case isn't addressed by this however, and that's to do with Ubuntu security updates. After #11 is merged and released, no code changes are required to upgrad... | True | rethink "statically tagged" images - _From @bacongobbler on September 23, 2016 9:0_
Our current tagging workflow for docker-base goes like this:
- PR a few new features
- tag it
- :shipit:
One use case isn't addressed by this however, and that's to do with Ubuntu security updates. After #11 is merged and released, n... | non_priority | rethink statically tagged images from bacongobbler on september our current tagging workflow for docker base goes like this pr a few new features tag it shipit one use case isn t addressed by this however and that s to do with ubuntu security updates after is merged and released no cod... | 0 |
321,313 | 23,850,189,633 | IssuesEvent | 2022-09-06 17:10:11 | pharmaverse/admiral | https://api.github.com/repos/pharmaverse/admiral | closed | Documentation: Typo on derive_vars_dtm | documentation good first issue release 0.8.0 05-Sep-2022 | ### Please select a category the issue is focused on?
_No response_
### Let us know where something needs a refresh or put your idea here!
On the [documentation page ](https://pharmaverse.github.io/admiral/reference/derive_vars_dtm.html) for this function, there is a an example given: impute_dtc(
"2020-11",
min_da... | 1.0 | Documentation: Typo on derive_vars_dtm - ### Please select a category the issue is focused on?
_No response_
### Let us know where something needs a refresh or put your idea here!
On the [documentation page ](https://pharmaverse.github.io/admiral/reference/derive_vars_dtm.html) for this function, there is a an exam... | non_priority | documentation typo on derive vars dtm please select a category the issue is focused on no response let us know where something needs a refresh or put your idea here on the for this function there is a an example given impute dtc min dates list ymd hms ymd hms ... | 0 |
228,146 | 17,420,317,880 | IssuesEvent | 2021-08-04 00:06:38 | ISS-Mimic/Mimic | https://api.github.com/repos/ISS-Mimic/Mimic | opened | Spec out 2-ft HDMI cables instead of 3-ft cables | Documentation | The cables listed in the [HDMI Cable BOM](https://github.com/ISS-Mimic/Mimic/wiki/Build-Instruction%3A-Bill-of-Materials#hdmi-cables) are for a 3-pack of 3-ft cables (qty 2). I didn't pay attention and ordered them, but they're really too long.
Suggest changing to [Cable Builders Short HDMI Cable 2-ft [2-Pack]](https... | 1.0 | Spec out 2-ft HDMI cables instead of 3-ft cables - The cables listed in the [HDMI Cable BOM](https://github.com/ISS-Mimic/Mimic/wiki/Build-Instruction%3A-Bill-of-Materials#hdmi-cables) are for a 3-pack of 3-ft cables (qty 2). I didn't pay attention and ordered them, but they're really too long.
Suggest changing to [C... | non_priority | spec out ft hdmi cables instead of ft cables the cables listed in the are for a pack of ft cables qty i didn t pay attention and ordered them but they re really too long suggest changing to qty it s a couple of dollars more overall but removes having hdmi cable looping out from the frame... | 0 |
28,800 | 12,965,919,216 | IssuesEvent | 2020-07-20 23:28:52 | dart-lang/dart-pad | https://api.github.com/repos/dart-lang/dart-pad | opened | Debug why dart-services fails after serving for a couple of hours | dart-services p1 | For reasons unknown, `dart-services` transitions into a failure state after serving content for a couple of hours. We need to find out why, and build a reproduction case for Dart DevTools team. | 1.0 | Debug why dart-services fails after serving for a couple of hours - For reasons unknown, `dart-services` transitions into a failure state after serving content for a couple of hours. We need to find out why, and build a reproduction case for Dart DevTools team. | non_priority | debug why dart services fails after serving for a couple of hours for reasons unknown dart services transitions into a failure state after serving content for a couple of hours we need to find out why and build a reproduction case for dart devtools team | 0 |
127,408 | 12,322,200,343 | IssuesEvent | 2020-05-13 09:56:50 | alphagov/cyber-security-nessus | https://api.github.com/repos/alphagov/cyber-security-nessus | closed | Create documentation | documentation | We need to have some basic documentation for this project. This will help explain how to work with the service for new team members a refresh the memory of anyone coming back to the project.
The documentation should include the following
- [] [ADR](https://github.com/joelparkerhenderson/architecture_decision_reco... | 1.0 | Create documentation - We need to have some basic documentation for this project. This will help explain how to work with the service for new team members a refresh the memory of anyone coming back to the project.
The documentation should include the following
- [] [ADR](https://github.com/joelparkerhenderson/arc... | non_priority | create documentation we need to have some basic documentation for this project this will help explain how to work with the service for new team members a refresh the memory of anyone coming back to the project the documentation should include the following records simple architecture diagram ... | 0 |
18,190 | 5,607,138,621 | IssuesEvent | 2017-04-01 02:20:58 | mcsheaj/SPEasyForms | https://api.github.com/repos/mcsheaj/SPEasyForms | closed | Save button doesn't work on root site | codeplex | **This issue was imported from [CodePlex](http://SPEasyForms.codeplex.com/workitem/8)**
**[ee61re](http://www.codeplex.com/site/users/view/ee61re)** wrote 2014-12-09 at 06:21
Environment is 2010 SP2 with November 2014 CU
web app with single site collection at root - was a 2007 content database attach-upgrad... | 1.0 | Save button doesn't work on root site - **This issue was imported from [CodePlex](http://SPEasyForms.codeplex.com/workitem/8)**
**[ee61re](http://www.codeplex.com/site/users/view/ee61re)** wrote 2014-12-09 at 06:21
Environment is 2010 SP2 with November 2014 CU
web app with single site collection at root - w... | non_priority | save button doesn t work on root site this issue was imported from wrote at environment is with november cu web app with single site collection at root was a content database attach upgrade to solution is account used is site collection administr... | 0 |
21,406 | 17,028,661,220 | IssuesEvent | 2021-07-04 04:46:00 | home-climate-control/dz | https://api.github.com/repos/home-climate-control/dz | opened | Make PID_Controller visible to JMX | JMX bug instrumentation usability | ### Expected Behavior
When added to `JmxWrapper`, the `PID_Controller` is accessible via `jconsole`.
### Actual Behavior
`PID_Controller` is not visible at `jconsole`.
### Root Cause
Not passing the JMX name to `AbstractPidController`. | True | Make PID_Controller visible to JMX - ### Expected Behavior
When added to `JmxWrapper`, the `PID_Controller` is accessible via `jconsole`.
### Actual Behavior
`PID_Controller` is not visible at `jconsole`.
### Root Cause
Not passing the JMX name to `AbstractPidController`. | non_priority | make pid controller visible to jmx expected behavior when added to jmxwrapper the pid controller is accessible via jconsole actual behavior pid controller is not visible at jconsole root cause not passing the jmx name to abstractpidcontroller | 0 |
235 | 2,587,974,420 | IssuesEvent | 2015-02-17 21:50:10 | uProxy/uproxy | https://api.github.com/repos/uProxy/uproxy | closed | month is wrong in logging timestamps | C:ServiceOrInfrastructure P2 | Logs from running Simple SOCKS this morning:
```
simple-socks I [1/17 12:46:21.356] SocksToRtc listening on: {"address":"127.0.0.1","port":9999}
lib/freedom/freedom-for-chrome.js:1111 simple-socks I [1/17 12:46:21.357] curl -x socks5h://127.0.0.1:9999 www.example.com
lib/freedom/freedom-for-chrome.js:1111 simpl... | 1.0 | month is wrong in logging timestamps - Logs from running Simple SOCKS this morning:
```
simple-socks I [1/17 12:46:21.356] SocksToRtc listening on: {"address":"127.0.0.1","port":9999}
lib/freedom/freedom-for-chrome.js:1111 simple-socks I [1/17 12:46:21.357] curl -x socks5h://127.0.0.1:9999 www.example.com
lib/fr... | non_priority | month is wrong in logging timestamps logs from running simple socks this morning simple socks i sockstortc listening on address port lib freedom freedom for chrome js simple socks i curl x lib freedom freedom for chrome js simple socks i rtctonet ready freed... | 0 |
89,788 | 15,837,540,456 | IssuesEvent | 2021-04-06 20:56:28 | TIBCOSoftware/tci-flogo | https://api.github.com/repos/TIBCOSoftware/tci-flogo | closed | WS-2019-0064 (High) detected in handlebars-3.0.3.tgz - autoclosed | security vulnerability | ## WS-2019-0064 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-3.0.3.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates ef... | True | WS-2019-0064 (High) detected in handlebars-3.0.3.tgz - autoclosed - ## WS-2019-0064 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-3.0.3.tgz</b></p></summary>
<p>Handlebars... | non_priority | ws high detected in handlebars tgz autoclosed ws high severity vulnerability vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href dependency hierarchy ... | 0 |
3,998 | 2,947,664,540 | IssuesEvent | 2015-07-05 10:40:40 | Glitchfiend/BiomesOPlenty | https://api.github.com/repos/Glitchfiend/BiomesOPlenty | closed | Unknown Recipe Class Warning | code | Apparently this is making some people scream as their log is not clean. | 1.0 | Unknown Recipe Class Warning - Apparently this is making some people scream as their log is not clean. | non_priority | unknown recipe class warning apparently this is making some people scream as their log is not clean | 0 |
4,741 | 17,369,742,066 | IssuesEvent | 2021-07-30 12:26:31 | dcaribou/player-scores | https://api.github.com/repos/dcaribou/player-scores | closed | Enable self-serve DVC backend access granting | automations | In order to be able to pull data from DVC remote storage, potential contributors need to be able to List and Get objects from S3 bucket `s3://player-scores`. Enable users to self-grant permissions for this actions by creating a PR adding their IAM user to a whitelist in the Terraform configuration.
Create a terrafo... | 1.0 | Enable self-serve DVC backend access granting - In order to be able to pull data from DVC remote storage, potential contributors need to be able to List and Get objects from S3 bucket `s3://player-scores`. Enable users to self-grant permissions for this actions by creating a PR adding their IAM user to a whitelist in ... | non_priority | enable self serve dvc backend access granting in order to be able to pull data from dvc remote storage potential contributors need to be able to list and get objects from bucket player scores enable users to self grant permissions for this actions by creating a pr adding their iam user to a whitelist in th... | 0 |
333,097 | 24,363,779,672 | IssuesEvent | 2022-10-03 13:45:14 | superstashed/medusa-stonkers | https://api.github.com/repos/superstashed/medusa-stonkers | closed | Update README.md so it matches the Hackathon guidelines | documentation | Update README.md so it matches the [Hackathon guidelines](https://github.com/suhailkakar/react-native-medusajs/blob/main/README.md) | 1.0 | Update README.md so it matches the Hackathon guidelines - Update README.md so it matches the [Hackathon guidelines](https://github.com/suhailkakar/react-native-medusajs/blob/main/README.md) | non_priority | update readme md so it matches the hackathon guidelines update readme md so it matches the | 0 |
221,811 | 24,659,159,454 | IssuesEvent | 2022-10-18 04:21:58 | valtech-ch/microservice-kubernetes-cluster | https://api.github.com/repos/valtech-ch/microservice-kubernetes-cluster | reopened | CVE-2020-10650 (High) detected in jackson-databind-2.9.8.jar | security vulnerability | ## CVE-2020-10650 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2020-10650 (High) detected in jackson-databind-2.9.8.jar - ## CVE-2020-10650 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General... | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file functions build gradle path ... | 0 |
54,213 | 13,265,076,575 | IssuesEvent | 2020-08-21 05:39:04 | microsoft/vscode | https://api.github.com/repos/microsoft/vscode | opened | Dependency cycle between 'vs/workbench/api/browser/mainThreadWebview' and 'vs/workbench/api/browser/mainThreadWebviewSerializer'. | important vscode-build | ```
There is a dependency cycle between 'vs/workbench/api/browser/mainThreadWebview' and 'vs/workbench/api/browser/mainThreadWebviewSerializer'. The cyclic path follows:
vs/workbench/api/browser/mainThreadWebview =>
vs/workbench/api/browser/mainThreadWebviewSerializer =>
vs/workbench/api/browser/mainThreadWebview... | 1.0 | Dependency cycle between 'vs/workbench/api/browser/mainThreadWebview' and 'vs/workbench/api/browser/mainThreadWebviewSerializer'. - ```
There is a dependency cycle between 'vs/workbench/api/browser/mainThreadWebview' and 'vs/workbench/api/browser/mainThreadWebviewSerializer'. The cyclic path follows:
vs/workbench/api... | non_priority | dependency cycle between vs workbench api browser mainthreadwebview and vs workbench api browser mainthreadwebviewserializer there is a dependency cycle between vs workbench api browser mainthreadwebview and vs workbench api browser mainthreadwebviewserializer the cyclic path follows vs workbench api... | 0 |
1,226 | 2,534,221,592 | IssuesEvent | 2015-01-24 18:42:58 | mathjax/MathJax | https://api.github.com/repos/mathjax/MathJax | closed | MathJax can't find its script tag in XHTML if XHTML tags use an explicit prefix | Accepted Merged QA - Do Not Write Automated Test | If I create an xhtml page that uses explicit prefixes on the html tags, MathJax's code for finding its `<script>` tag fails. There also seems to be a similar issue with the `<head>` tag.
Test case:
```html
<html:html xmlns:html="http://www.w3.org/1999/xhtml" xmlns="http://www.w3.org/1999/xhtml">
<html:head>
... | 1.0 | MathJax can't find its script tag in XHTML if XHTML tags use an explicit prefix - If I create an xhtml page that uses explicit prefixes on the html tags, MathJax's code for finding its `<script>` tag fails. There also seems to be a similar issue with the `<head>` tag.
Test case:
```html
<html:html xmlns:html="htt... | non_priority | mathjax can t find its script tag in xhtml if xhtml tags use an explicit prefix if i create an xhtml page that uses explicit prefixes on the html tags mathjax s code for finding its tag fails there also seems to be a similar issue with the tag test case html html html xmlns html xmlns ... | 0 |
174,456 | 21,300,072,525 | IssuesEvent | 2022-04-15 01:03:48 | shaimael/easybuggy2 | https://api.github.com/repos/shaimael/easybuggy2 | closed | CVE-2020-2875 (Medium) detected in mysql-connector-java-5.1.25.jar - autoclosed | security vulnerability | ## CVE-2020-2875 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p></summary>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http... | True | CVE-2020-2875 (Medium) detected in mysql-connector-java-5.1.25.jar - autoclosed - ## CVE-2020-2875 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b><... | non_priority | cve medium detected in mysql connector java jar autoclosed cve medium severity vulnerability vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to dependency file pom xml path to vulnerable library repository mysql ... | 0 |
396,462 | 27,119,454,659 | IssuesEvent | 2023-02-15 21:26:53 | motion-canvas/motion-canvas | https://api.github.com/repos/motion-canvas/motion-canvas | closed | Documentation for logging | b-documentation c-accepted a-docs | **Description**
Since the Question arose a couple of times in the Discord and asked myself the same thing recently, it would be good
to have a short introduction / guide on how to use the build in logger, so the messages get displayed in the UI.
Doesn't have to be long since there is not much to write about, but I... | 1.0 | Documentation for logging - **Description**
Since the Question arose a couple of times in the Discord and asked myself the same thing recently, it would be good
to have a short introduction / guide on how to use the build in logger, so the messages get displayed in the UI.
Doesn't have to be long since there is no... | non_priority | documentation for logging description since the question arose a couple of times in the discord and asked myself the same thing recently it would be good to have a short introduction guide on how to use the build in logger so the messages get displayed in the ui doesn t have to be long since there is no... | 0 |
138,819 | 31,035,159,833 | IssuesEvent | 2023-08-10 14:48:19 | ljnpng/algorithm | https://api.github.com/repos/ljnpng/algorithm | opened | 289.生命游戏 | leetcode | # 289.生命游戏
[https://leetcode.cn/problems/game-of-life](https://leetcode.cn/problems/game-of-life)
## 原题
根据 <a href="https://baike.baidu.com/item/%E7%94%9F%E5%91%BD%E6%B8%B8%E6%88%8F/2926434?fr=aladdin" target="_blank">百度百科</a> , **生命游戏** ,简称为 **生命** ,是英国数学家约翰·何顿·康威在 1970 年发明的细胞自动机。
给定一个包含 `m × n` 个格子的面板,每一个格子都可以看成是一个细... | 1.0 | 289.生命游戏 - # 289.生命游戏
[https://leetcode.cn/problems/game-of-life](https://leetcode.cn/problems/game-of-life)
## 原题
根据 <a href="https://baike.baidu.com/item/%E7%94%9F%E5%91%BD%E6%B8%B8%E6%88%8F/2926434?fr=aladdin" target="_blank">百度百科</a> , **生命游戏** ,简称为 **生命** ,是英国数学家约翰·何顿·康威在 1970 年发明的细胞自动机。
给定一个包含 `m × n` 个格子的面板,每一个... | non_priority | 生命游戏 生命游戏 原题 根据 百度百科 , 生命游戏 ,简称为 生命 ,是英国数学家约翰·何顿·康威在 年发明的细胞自动机。 给定一个包含 m × n 个格子的面板,每一个格子都可以看成是一个细胞。每个细胞都具有一个初始状态: 即为 活细胞 (live),或 即为 死细胞 (dead)。每个细胞与其八个相邻位置(水平,垂直,对角线)的细胞都遵循以下四条生存定律: 如果活细胞周围八个位置的活细胞数少于两个,则该位置活细胞死亡; 如果活细胞周围八个位置有两个或三个活细胞,则该位置活细胞仍然存活; 如果活细胞周围八个位置有超过三个活细... | 0 |
24,917 | 12,195,271,417 | IssuesEvent | 2020-04-29 17:05:49 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | opened | DTS Discovery Day 🚀 | Service: Apps Service: Dev Service: Product Type: Research Workgroup: DTS | This epic compiles projects for [DTS' Discovery Day on May 1, 2020](https://docs.google.com/presentation/d/1aSqnnvi3XG2njeU7Zbsc23ZEe96VSHUDyxPjrB6O5D0/edit?usp=sharing). Please add a Github issue to capture what you plan to work on!
Here's a template you can start from if you'd like:
### Challenge
What is the probl... | 3.0 | DTS Discovery Day 🚀 - This epic compiles projects for [DTS' Discovery Day on May 1, 2020](https://docs.google.com/presentation/d/1aSqnnvi3XG2njeU7Zbsc23ZEe96VSHUDyxPjrB6O5D0/edit?usp=sharing). Please add a Github issue to capture what you plan to work on!
Here's a template you can start from if you'd like:
### Chal... | non_priority | dts discovery day 🚀 this epic compiles projects for please add a github issue to capture what you plan to work on here s a template you can start from if you d like challenge what is the problem you want to solve or solution you want to explore prerequisites software data getting a local dev en... | 0 |
447,284 | 31,681,173,510 | IssuesEvent | 2023-09-08 00:00:15 | danthegoodman1/icedb | https://api.github.com/repos/danthegoodman1/icedb | opened | Performance test (against BQ) | documentation | Github events has 232M rows and lots of example queries: https://ghe.clickhouse.tech/
https://clickhouse.com/docs/en/getting-started/example-datasets/nyc-taxi has 3B rows but is smaller in size can do this too and much less complex schema
Should run the same queries against. We can leave bigquery for 5+ hours (ma... | 1.0 | Performance test (against BQ) - Github events has 232M rows and lots of example queries: https://ghe.clickhouse.tech/
https://clickhouse.com/docs/en/getting-started/example-datasets/nyc-taxi has 3B rows but is smaller in size can do this too and much less complex schema
Should run the same queries against. We can... | non_priority | performance test against bq github events has rows and lots of example queries has rows but is smaller in size can do this too and much less complex schema should run the same queries against we can leave bigquery for hours maybe even days to merge and fully merge up icedb record the performa... | 0 |
78,785 | 7,668,906,646 | IssuesEvent | 2018-05-14 07:54:13 | NationalBankBelgium/stark | https://api.github.com/repos/NationalBankBelgium/stark | opened | stark-testing: simplify the way Karma typescript default config can be customized | comp: testing must type: refactor | <!-- Note: for support questions please use Stack Overflow: https://stackoverflow.com/questions/tagged/stark -->
## I'm submitting a...
<!-- Check one of the following options with "x" -->
<pre><code>
[ ] Regression (a behavior that used to work and stopped working in a new release)
[ ] Bug report <!-- Please s... | 1.0 | stark-testing: simplify the way Karma typescript default config can be customized - <!-- Note: for support questions please use Stack Overflow: https://stackoverflow.com/questions/tagged/stark -->
## I'm submitting a...
<!-- Check one of the following options with "x" -->
<pre><code>
[ ] Regression (a behavior th... | non_priority | stark testing simplify the way karma typescript default config can be customized i m submitting a regression a behavior that used to work and stopped working in a new release bug report feature request documentation issue or request support request please do not submit suppor... | 0 |
61,499 | 14,627,778,420 | IssuesEvent | 2020-12-23 12:57:24 | bitbar/test-samples | https://api.github.com/repos/bitbar/test-samples | opened | CVE-2018-12536 (Medium) detected in jetty-util-9.4.1.v20170120.jar | security vulnerability | ## CVE-2018-12536 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jetty-util-9.4.1.v20170120.jar</b></p></summary>
<p>Utility classes for Jetty</p>
<p>Library home page: <a href="htt... | True | CVE-2018-12536 (Medium) detected in jetty-util-9.4.1.v20170120.jar - ## CVE-2018-12536 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jetty-util-9.4.1.v20170120.jar</b></p></summary>... | non_priority | cve medium detected in jetty util jar cve medium severity vulnerability vulnerable library jetty util jar utility classes for jetty library home page a href path to dependency file test samples samples testing frameworks appium server side image recognition pom xml ... | 0 |
340,510 | 30,522,049,128 | IssuesEvent | 2023-07-19 08:45:03 | wizardsardine/liana | https://api.github.com/repos/wizardsardine/liana | opened | `test_retry_workqueue_exceeded` can be flaky in CI | Tests | Sometimes the workqueue exceeded doesn't show up. See https://github.com/wizardsardine/liana/pull/569/checks?check_run_id=15140031960. | 1.0 | `test_retry_workqueue_exceeded` can be flaky in CI - Sometimes the workqueue exceeded doesn't show up. See https://github.com/wizardsardine/liana/pull/569/checks?check_run_id=15140031960. | non_priority | test retry workqueue exceeded can be flaky in ci sometimes the workqueue exceeded doesn t show up see | 0 |
125,910 | 10,369,006,295 | IssuesEvent | 2019-09-07 21:59:25 | Rocologo/MobHunting | https://api.github.com/repos/Rocologo/MobHunting | closed | lore edit issue | Fixed - To be tested | Hello, been using this for a long time, however is it possible to setup log when player exchange their bag of money using sign? I have players use change lore method to edit the bag of gold and exchanged over 1 trillion amount of money, i need to close my server to shut down this bug | 1.0 | lore edit issue - Hello, been using this for a long time, however is it possible to setup log when player exchange their bag of money using sign? I have players use change lore method to edit the bag of gold and exchanged over 1 trillion amount of money, i need to close my server to shut down this bug | non_priority | lore edit issue hello been using this for a long time however is it possible to setup log when player exchange their bag of money using sign i have players use change lore method to edit the bag of gold and exchanged over trillion amount of money i need to close my server to shut down this bug | 0 |
178,934 | 21,509,586,153 | IssuesEvent | 2022-04-28 01:57:26 | emilwareus/generator-jhipster | https://api.github.com/repos/emilwareus/generator-jhipster | closed | CVE-2019-15657 (High) detected in eslint-utils-1.3.1.tgz - autoclosed | security vulnerability | ## CVE-2019-15657 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>eslint-utils-1.3.1.tgz</b></p></summary>
<p>Utilities for ESLint plugins.</p>
<p>Library home page: <a href="https://r... | True | CVE-2019-15657 (High) detected in eslint-utils-1.3.1.tgz - autoclosed - ## CVE-2019-15657 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>eslint-utils-1.3.1.tgz</b></p></summary>
<p>Ut... | non_priority | cve high detected in eslint utils tgz autoclosed cve high severity vulnerability vulnerable library eslint utils tgz utilities for eslint plugins library home page a href path to dependency file package json path to vulnerable library node modules eslint utils p... | 0 |
54,248 | 13,496,254,703 | IssuesEvent | 2020-09-12 02:44:24 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | Email invites land on welcome page with guest disabled | bug defect p1 type:invite type:threepids | If Riot's default HS doesn't have guest access enabled, clicking through on an email invite just lands you on the welcome page with no mention of the room or invite or anything. | 1.0 | Email invites land on welcome page with guest disabled - If Riot's default HS doesn't have guest access enabled, clicking through on an email invite just lands you on the welcome page with no mention of the room or invite or anything. | non_priority | email invites land on welcome page with guest disabled if riot s default hs doesn t have guest access enabled clicking through on an email invite just lands you on the welcome page with no mention of the room or invite or anything | 0 |
51,272 | 10,605,381,105 | IssuesEvent | 2019-10-10 20:20:30 | mumble-voip/mumble | https://api.github.com/repos/mumble-voip/mumble | closed | Q: Audio input/output | audio code mumble | I am currently writing the audio hooks for the new plugin framework but I need to get some more info on how the audio PCM arrays are structured.
Condensed I think the question boils down to this:
1. Is the AudioInput in Mumble always mono (only one channel)? If not how many channels does it have and how many sample... | 1.0 | Q: Audio input/output - I am currently writing the audio hooks for the new plugin framework but I need to get some more info on how the audio PCM arrays are structured.
Condensed I think the question boils down to this:
1. Is the AudioInput in Mumble always mono (only one channel)? If not how many channels does it ... | non_priority | q audio input output i am currently writing the audio hooks for the new plugin framework but i need to get some more info on how the audio pcm arrays are structured condensed i think the question boils down to this is the audioinput in mumble always mono only one channel if not how many channels does it ... | 0 |
324,322 | 27,800,763,565 | IssuesEvent | 2023-03-17 15:40:42 | phetsims/qa | https://api.github.com/repos/phetsims/qa | opened | Dev Test: Calculus Grapher 1.0.0-dev.TBD | QA:dev-test | <!---
////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////
DEVELOPERS:
* title for this issue = Dev Test: {{SIM_TITLE}} {{VERSION}}
* replace {{MENTIONS}} with @mentions for team members who should received GitHub notifications about this issu... | 1.0 | Dev Test: Calculus Grapher 1.0.0-dev.TBD - <!---
////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////
DEVELOPERS:
* title for this issue = Dev Test: {{SIM_TITLE}} {{VERSION}}
* replace {{MENTIONS}} with @mentions for team members who should re... | non_priority | dev test calculus grapher dev tbd developers title for this issue dev test sim title version replace mentions with mentions for team members who should re... | 0 |
40,147 | 20,602,690,418 | IssuesEvent | 2022-03-06 14:11:40 | sl-lang/sll | https://api.github.com/repos/sl-lang/sll | opened | Make the scheduler run on multiple OS threads | internal performance vm | Make the scheduler execute tasks on every CPU core to improve concurrency. | True | Make the scheduler run on multiple OS threads - Make the scheduler execute tasks on every CPU core to improve concurrency. | non_priority | make the scheduler run on multiple os threads make the scheduler execute tasks on every cpu core to improve concurrency | 0 |
64,221 | 26,654,793,534 | IssuesEvent | 2023-01-25 16:05:40 | SigNoz/signoz | https://api.github.com/repos/SigNoz/signoz | closed | Deprecate http code, grpc status code, grpc method | duplicate frontend query-service deprecation | We have migrated to using common column called Status Code for http, grpc, rpc. Also grpc method to rpc method.
Otel collector issue: https://github.com/SigNoz/signoz-otel-collector/issues/42 | 1.0 | Deprecate http code, grpc status code, grpc method - We have migrated to using common column called Status Code for http, grpc, rpc. Also grpc method to rpc method.
Otel collector issue: https://github.com/SigNoz/signoz-otel-collector/issues/42 | non_priority | deprecate http code grpc status code grpc method we have migrated to using common column called status code for http grpc rpc also grpc method to rpc method otel collector issue | 0 |
163,976 | 25,902,408,449 | IssuesEvent | 2022-12-15 07:19:23 | keypom/keypom-airfoil | https://api.github.com/repos/keypom/keypom-airfoil | closed | [Layout] - Navbar | design system | # Describe the feature you would like to request
Navbar for page navigation
# Provide a brief explanation of why this feature is necessary
For user to navigate around Keypom
# Provide an estimation of how long the developers should spend on implementing this feature
1 - 3 hours
# References
 | automation enhancement | "report-dir" argument for specifying junit tests output directory - can be removed, including any references that uses it (also in Docs):
https://github.com/submariner-io/submariner/blob/06332b91b193c0ab362e7f0a96cd715b8556acd5/test/e2e/framework/test_context.go#L40
Ginkgo has this feature already, for example
--g... | 1.0 | "report-dir" argument can be removed (Ginkgo has --reportFile option) - "report-dir" argument for specifying junit tests output directory - can be removed, including any references that uses it (also in Docs):
https://github.com/submariner-io/submariner/blob/06332b91b193c0ab362e7f0a96cd715b8556acd5/test/e2e/framework/... | non_priority | report dir argument can be removed ginkgo has reportfile option report dir argument for specifying junit tests output directory can be removed including any references that uses it also in docs ginkgo has this feature already for example ginkgo reportfile workdir junit result xml | 0 |
270,472 | 28,960,725,171 | IssuesEvent | 2023-05-10 02:04:58 | mattdanielbrown/primed | https://api.github.com/repos/mattdanielbrown/primed | closed | CVE-2020-7751 (High) detected in pathval-1.1.0.tgz - autoclosed | Mend: dependency security vulnerability | ## CVE-2020-7751 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>pathval-1.1.0.tgz</b></p></summary>
<p>Object value retrieval given a string path</p>
<p>Library home page: <a href="ht... | True | CVE-2020-7751 (High) detected in pathval-1.1.0.tgz - autoclosed - ## CVE-2020-7751 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>pathval-1.1.0.tgz</b></p></summary>
<p>Object value r... | non_priority | cve high detected in pathval tgz autoclosed cve high severity vulnerability vulnerable library pathval tgz object value retrieval given a string path library home page a href path to dependency file package json path to vulnerable library node modules pathval pac... | 0 |
263,393 | 28,030,108,621 | IssuesEvent | 2023-03-28 11:50:06 | RG4421/ampere-centos-kernel | https://api.github.com/repos/RG4421/ampere-centos-kernel | reopened | CVE-2020-15437 (Medium) detected in linuxv5.2 | Mend: dependency security vulnerability | ## CVE-2020-15437 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv5.2</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/tor... | True | CVE-2020-15437 (Medium) detected in linuxv5.2 - ## CVE-2020-15437 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv5.2</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>L... | non_priority | cve medium detected in cve medium severity vulnerability vulnerable library linux kernel source tree library home page a href found in base branch amp centos kernel vulnerable source files drivers tty serial core c drivers tty ... | 0 |
328,412 | 28,118,248,871 | IssuesEvent | 2023-03-31 12:28:44 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: tpcc/mixed-headroom/n5cpu16 failed | C-test-failure O-robot O-roachtest branch-master release-blocker T-testeng | roachtest.tpcc/mixed-headroom/n5cpu16 [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/9329887?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/9329887?buildTab=artifacts#/tpcc/mixed-h... | 3.0 | roachtest: tpcc/mixed-headroom/n5cpu16 failed - roachtest.tpcc/mixed-headroom/n5cpu16 [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/9329887?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyG... | non_priority | roachtest tpcc mixed headroom failed roachtest tpcc mixed headroom with on master test artifacts and logs in artifacts tpcc mixed headroom run monitor go wait monitor failure monitor task failed output in run cockroach workload r cockroach workload run tpcc warehouses ... | 0 |
74,883 | 25,382,122,445 | IssuesEvent | 2022-11-21 18:27:05 | bcpierce00/unison | https://api.github.com/repos/bcpierce00/unison | closed | macOS: failure to propagate changes when file extension is hidden | defect wontfix impact-low feedback macOS | ## Problem
Unison properly identifies differences but fails to propagate changes for files that have the "hide extension" box checked. An example error output:
```
Docs/docname.pdf
Error in setting file information:
Operation not permitted [setattrlist(/Users/<redacted>/Docs/.unison.docname.pdf.b521af74258495965... | 1.0 | macOS: failure to propagate changes when file extension is hidden - ## Problem
Unison properly identifies differences but fails to propagate changes for files that have the "hide extension" box checked. An example error output:
```
Docs/docname.pdf
Error in setting file information:
Operation not permitted [seta... | non_priority | macos failure to propagate changes when file extension is hidden problem unison properly identifies differences but fails to propagate changes for files that have the hide extension box checked an example error output docs docname pdf error in setting file information operation not permitted ... | 0 |
221,130 | 16,995,095,471 | IssuesEvent | 2021-07-01 04:51:47 | faridlesosibirsk/TrainingRepository | https://api.github.com/repos/faridlesosibirsk/TrainingRepository | opened | 36. Несколько репозиториев | documentation | Написать заголовок и цель. Ответ сохранить в файл "36. Несколько репозиториев.md". | 1.0 | 36. Несколько репозиториев - Написать заголовок и цель. Ответ сохранить в файл "36. Несколько репозиториев.md". | non_priority | несколько репозиториев написать заголовок и цель ответ сохранить в файл несколько репозиториев md | 0 |
225,090 | 24,807,959,383 | IssuesEvent | 2022-10-25 07:04:29 | sast-automation-dev/openidm-community-edition-45 | https://api.github.com/repos/sast-automation-dev/openidm-community-edition-45 | opened | activiti-engine-5.10.jar: 3 vulnerabilities (highest severity is: 8.1) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>activiti-engine-5.10.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /openidm-workflow-activiti/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner... | True | activiti-engine-5.10.jar: 3 vulnerabilities (highest severity is: 8.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>activiti-engine-5.10.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /openidm-workf... | non_priority | activiti engine jar vulnerabilities highest severity is vulnerable library activiti engine jar path to dependency file openidm workflow activiti pom xml path to vulnerable library home wss scanner repository org mybatis mybatis mybatis jar home wss scanner rep... | 0 |
136,807 | 19,981,701,194 | IssuesEvent | 2022-01-30 01:33:02 | Tech-Start-UCalgary/Aquavolution | https://api.github.com/repos/Tech-Start-UCalgary/Aquavolution | closed | Add death scene | enhancement design | When the player ded switch to the "Death Scene" that displays "You died" with your Score in the middle (for now at least) | 1.0 | Add death scene - When the player ded switch to the "Death Scene" that displays "You died" with your Score in the middle (for now at least) | non_priority | add death scene when the player ded switch to the death scene that displays you died with your score in the middle for now at least | 0 |
54,081 | 7,872,858,799 | IssuesEvent | 2018-06-25 12:41:26 | philippkraft/cmf | https://api.github.com/repos/philippkraft/cmf | opened | Technical Flux and Waterbalance Tutorials need reworking | documentation help wanted | The states of the Technical Flux / Waterbalance Tutorials are confusing and need a total rewrite. Otherwise learning users do not understand the behaviour as #44 shows. | 1.0 | Technical Flux and Waterbalance Tutorials need reworking - The states of the Technical Flux / Waterbalance Tutorials are confusing and need a total rewrite. Otherwise learning users do not understand the behaviour as #44 shows. | non_priority | technical flux and waterbalance tutorials need reworking the states of the technical flux waterbalance tutorials are confusing and need a total rewrite otherwise learning users do not understand the behaviour as shows | 0 |
13,871 | 16,598,103,120 | IssuesEvent | 2021-06-01 15:39:13 | EwyBoy/OreTweaker | https://api.github.com/repos/EwyBoy/OreTweaker | opened | [Compatibility] Create | Compatibility Request | **Name of mod you want compatibility with?**
Create
**Is your compatibility request related to a problem?**
I will fix the issues people have with trying to disable ore generation from Create.
**Describe the solution you'd like**
A hardcoded check if Create is present then we can hook into its ore gen features... | True | [Compatibility] Create - **Name of mod you want compatibility with?**
Create
**Is your compatibility request related to a problem?**
I will fix the issues people have with trying to disable ore generation from Create.
**Describe the solution you'd like**
A hardcoded check if Create is present then we can hook ... | non_priority | create name of mod you want compatibility with create is your compatibility request related to a problem i will fix the issues people have with trying to disable ore generation from create describe the solution you d like a hardcoded check if create is present then we can hook into its ore g... | 0 |
62,982 | 7,661,067,000 | IssuesEvent | 2018-05-11 13:03:42 | chili-epfl/FROG | https://api.github.com/repos/chili-epfl/FROG | closed | Preview full-screen mode single activity hides top | design/UI | If you have a single activity open in preview, and you go to full-screen mode, the top of the activity is overlaid by the top bar.
Compare below.
There is also something weird about the container for the activity (the modal-body or whatever) - it's at 85% of the screen height for some reason - even more clear whe... | 1.0 | Preview full-screen mode single activity hides top - If you have a single activity open in preview, and you go to full-screen mode, the top of the activity is overlaid by the top bar.
Compare below.
There is also something weird about the container for the activity (the modal-body or whatever) - it's at 85% of th... | non_priority | preview full screen mode single activity hides top if you have a single activity open in preview and you go to full screen mode the top of the activity is overlaid by the top bar compare below there is also something weird about the container for the activity the modal body or whatever it s at of the... | 0 |
323,790 | 27,752,465,319 | IssuesEvent | 2023-03-15 22:03:32 | antrea-io/antrea | https://api.github.com/repos/antrea-io/antrea | closed | test-multicluster-e2e always failed | area/test/e2e kind/bug area/multi-cluster | **Describe the bug**
test-multicluster-e2e failed.
```
=== RUN TestConnectivity/TestMCService/Case=StretchedNetworkPolicy
time="2023-02-17T01:13:01Z" level=info msg="Creating/updating ClusterNetworkPolicy drop-client-pod-sel"
service_test.go:238:
Error Trace: /var/lib/jenkins/workspace/antrea-mult... | 1.0 | test-multicluster-e2e always failed - **Describe the bug**
test-multicluster-e2e failed.
```
=== RUN TestConnectivity/TestMCService/Case=StretchedNetworkPolicy
time="2023-02-17T01:13:01Z" level=info msg="Creating/updating ClusterNetworkPolicy drop-client-pod-sel"
service_test.go:238:
Error Trace: ... | non_priority | test multicluster always failed describe the bug test multicluster failed run testconnectivity testmcservice case stretchednetworkpolicy time level info msg creating updating clusternetworkpolicy drop client pod sel service test go error trace var lib jenkins ... | 0 |
87,882 | 11,008,071,790 | IssuesEvent | 2019-12-04 09:48:59 | devanshj/cogni | https://api.github.com/repos/devanshj/cogni | closed | Incremental output | design-issue enhancement | What should be done in the case of `python -c "while True: print('hello')"`? Currently there is no output because the process never exits. | 1.0 | Incremental output - What should be done in the case of `python -c "while True: print('hello')"`? Currently there is no output because the process never exits. | non_priority | incremental output what should be done in the case of python c while true print hello currently there is no output because the process never exits | 0 |
139,747 | 11,276,934,872 | IssuesEvent | 2020-01-15 00:56:38 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | opened | webcompat reporter not remembering if a website has already been reported | QA/Test-Plan-Specified QA/Yes bug feature/shields/webcompat | <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL GET THE ISSUE CLOSED. IT WILL ONLY BE REOPENED AFTER SUFFICIENT INFO IS PROV... | 1.0 | webcompat reporter not remembering if a website has already been reported - <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL ... | non_priority | webcompat reporter not remembering if a website has already been reported have you searched for similar issues before submitting this issue please check the open issues and add a note before logging a new issue please use the template below to provide information about the issue insufficient info will ... | 0 |
30,675 | 11,842,020,251 | IssuesEvent | 2020-03-23 22:02:06 | Mohib-hub/karate | https://api.github.com/repos/Mohib-hub/karate | opened | CVE-2019-12814 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2019-12814 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.8.5.jar</b>, <b>jackson-databind-2.8.8.jar</b>, <b>jackson-databind-2.9.8.jar</b></p></summary>
... | True | CVE-2019-12814 (Medium) detected in multiple libraries - ## CVE-2019-12814 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.8.5.jar</b>, <b>jackson-databind-2.8.8.... | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries jackson databind jar jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming... | 0 |
71,625 | 15,207,811,896 | IssuesEvent | 2021-02-17 01:04:35 | billmcchesney1/foxtrot | https://api.github.com/repos/billmcchesney1/foxtrot | closed | CVE-2020-27218 (Medium) detected in jetty-server-9.4.18.v20190429.jar, jetty-server-9.4.11.v20180605.jar - autoclosed | security vulnerability | ## CVE-2020-27218 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jetty-server-9.4.18.v20190429.jar</b>, <b>jetty-server-9.4.11.v20180605.jar</b></p></summary>
<p>
<details><summar... | True | CVE-2020-27218 (Medium) detected in jetty-server-9.4.18.v20190429.jar, jetty-server-9.4.11.v20180605.jar - autoclosed - ## CVE-2020-27218 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries ... | non_priority | cve medium detected in jetty server jar jetty server jar autoclosed cve medium severity vulnerability vulnerable libraries jetty server jar jetty server jar jetty server jar the core jetty server artifact library home page a href ... | 0 |
50,937 | 7,644,854,767 | IssuesEvent | 2018-05-08 16:41:59 | jiscdev/analytics-udd | https://api.github.com/repos/jiscdev/analytics-udd | closed | UDD Field Guide template: level of priority column | Documentation change | Craig and I have been working on the UDD Field Guide spreadsheet template, using the Tribal SI one as a case. We have 2 slightly conflicting requirements, 1 for validation and 1 for informing consumers about the level of priority of data items.
Validation: for validation purposes, we can use Mandatory and Optional (... | 1.0 | UDD Field Guide template: level of priority column - Craig and I have been working on the UDD Field Guide spreadsheet template, using the Tribal SI one as a case. We have 2 slightly conflicting requirements, 1 for validation and 1 for informing consumers about the level of priority of data items.
Validation: for val... | non_priority | udd field guide template level of priority column craig and i have been working on the udd field guide spreadsheet template using the tribal si one as a case we have slightly conflicting requirements for validation and for informing consumers about the level of priority of data items validation for val... | 0 |
82,711 | 15,679,665,276 | IssuesEvent | 2021-03-25 01:03:10 | rsoreq/WebGoat | https://api.github.com/repos/rsoreq/WebGoat | opened | CVE-2020-28503 (High) detected in copy-props-2.0.4.tgz | security vulnerability | ## CVE-2020-28503 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>copy-props-2.0.4.tgz</b></p></summary>
<p>Copy properties deeply between two objects.</p>
<p>Library home page: <a hre... | True | CVE-2020-28503 (High) detected in copy-props-2.0.4.tgz - ## CVE-2020-28503 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>copy-props-2.0.4.tgz</b></p></summary>
<p>Copy properties dee... | non_priority | cve high detected in copy props tgz cve high severity vulnerability vulnerable library copy props tgz copy properties deeply between two objects library home page a href path to dependency file webgoat docs package json path to vulnerable library webgoat docs node m... | 0 |
302,845 | 26,167,160,899 | IssuesEvent | 2023-01-01 12:38:53 | valory-xyz/open-autonomy | https://api.github.com/repos/valory-xyz/open-autonomy | closed | `TestTermination` not passing Tendermint health check | test |
This is a new issue but frequently recurring issue as of recently. Currently seen on PR #1620, #1621 and main: CI run [#6186](https://github.com/valory-xyz/open-autonomy/actions/runs/3630510890/jobs/6124133371).
In all cases this concerns `test_register_reset.TestTermination`
snippet: [failure.log](https://gith... | 1.0 | `TestTermination` not passing Tendermint health check -
This is a new issue but frequently recurring issue as of recently. Currently seen on PR #1620, #1621 and main: CI run [#6186](https://github.com/valory-xyz/open-autonomy/actions/runs/3630510890/jobs/6124133371).
In all cases this concerns `test_register_reset... | non_priority | testtermination not passing tendermint health check this is a new issue but frequently recurring issue as of recently currently seen on pr and main ci run in all cases this concerns test register reset testtermination snippet | 0 |
348,680 | 31,709,166,942 | IssuesEvent | 2023-09-09 03:53:47 | ValveSoftware/steam-for-linux | https://api.github.com/repos/ValveSoftware/steam-for-linux | closed | Steam Overlay: Error calling method from signal 'leaderboard_score_uploaded' | 3rd party game Need Retest | #### Your system information
<details><summary>Steam client version (build number or date)</summary>
<p>
```
Steam Version: 1690583737
Steam Client Build Date: Fri, Jul 28 20:44 UTC -08:00
Steam Web Build Date: Sat, Jul 29 00:21 UTC -08:00
Steam API Version: SteamClient020
```
</p>
</details>
* Distr... | 1.0 | Steam Overlay: Error calling method from signal 'leaderboard_score_uploaded' - #### Your system information
<details><summary>Steam client version (build number or date)</summary>
<p>
```
Steam Version: 1690583737
Steam Client Build Date: Fri, Jul 28 20:44 UTC -08:00
Steam Web Build Date: Sat, Jul 29 00:21 UT... | non_priority | steam overlay error calling method from signal leaderboard score uploaded your system information steam client version build number or date steam version steam client build date fri jul utc steam web build date sat jul utc steam api version ... | 0 |
413,400 | 27,950,644,270 | IssuesEvent | 2023-03-24 08:34:25 | nonebot/nonebot2 | https://api.github.com/repos/nonebot/nonebot2 | closed | Docs: NoneBot2文档改进计划 | documentation help wanted | # NoneBot2文档改进计划
Related: #3 ~~#372~~
## 描述问题或主题
NoneBot2文档由于一些原因~~主要是我们语文太菜~~,它的撰写方法存在各种问题,对新手的理解和使用造成了困难。
我们在这里希望对NoneBot现有的文档结构作出一点改进。
但是这不是我们几位开发者能够完成的。
我们都是普通人,在完成学习和工作之余维护项目代码和文档,实在感觉有些分身乏术。
**我们衷心希望,看到这个issue的每一个人,都为这个文档,作出一份自己的贡献。**
**而一份好的文档,需要你们每个人的帮助。**
<details>
<summary>不太正经的话</summar... | 1.0 | Docs: NoneBot2文档改进计划 - # NoneBot2文档改进计划
Related: #3 ~~#372~~
## 描述问题或主题
NoneBot2文档由于一些原因~~主要是我们语文太菜~~,它的撰写方法存在各种问题,对新手的理解和使用造成了困难。
我们在这里希望对NoneBot现有的文档结构作出一点改进。
但是这不是我们几位开发者能够完成的。
我们都是普通人,在完成学习和工作之余维护项目代码和文档,实在感觉有些分身乏术。
**我们衷心希望,看到这个issue的每一个人,都为这个文档,作出一份自己的贡献。**
**而一份好的文档,需要你们每个人的帮助。**
<details>
... | non_priority | docs related 描述问题或主题 主要是我们语文太菜 ,它的撰写方法存在各种问题,对新手的理解和使用造成了困难。 我们在这里希望对nonebot现有的文档结构作出一点改进。 但是这不是我们几位开发者能够完成的。 我们都是普通人,在完成学习和工作之余维护项目代码和文档,实在感觉有些分身乏术。 我们衷心希望,看到这个issue的每一个人,都为这个文档,作出一份自己的贡献。 而一份好的文档,需要你们每个人的帮助。 不太正经的话 我写这么多,要是没人来做我好尴尬啊…… 来贡献文... | 0 |
116,466 | 11,913,593,251 | IssuesEvent | 2020-03-31 12:16:42 | workarea-commerce/workarea | https://api.github.com/repos/workarea-commerce/workarea | closed | Feedback for "Fulfillment SKUs" doc | documentation | Feedback for "Fulfillment SKUs" (/articles/fulfillment-skus.html):
I find a typo on your documentation page https://developer.workarea.com/articles/fulfillment-skus.html#custom-fulfillment-policies
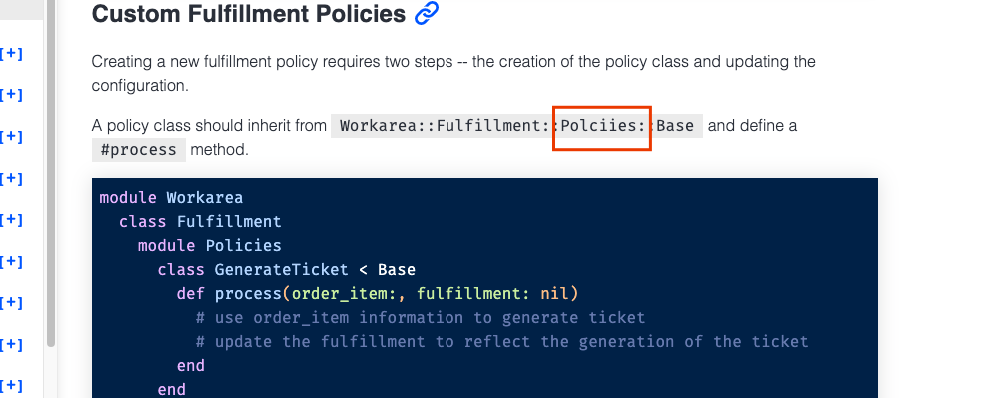
Than... | 1.0 | Feedback for "Fulfillment SKUs" doc - Feedback for "Fulfillment SKUs" (/articles/fulfillment-skus.html):
I find a typo on your documentation page https://developer.workarea.com/articles/fulfillment-skus.html#custom-fulfillment-policies
 | 1.0 | Extend README with some initial information - * Express the use-case of the project
* Add NEAR Indexer link
* Provide build instructions (or reference to a relevant NEAR Indexer section if that is the same) | non_priority | extend readme with some initial information express the use case of the project add near indexer link provide build instructions or reference to a relevant near indexer section if that is the same | 0 |
155,785 | 24,518,440,878 | IssuesEvent | 2022-10-11 07:39:18 | JokeNetwork/faq | https://api.github.com/repos/JokeNetwork/faq | closed | Change CSS to Primer | DESIGN no-issue-activity | ## Proposed changes
Since the project is mainly design to look like a GitHub page, we should use [Primer](https://github.com/primer/css) in the future. | 1.0 | Change CSS to Primer - ## Proposed changes
Since the project is mainly design to look like a GitHub page, we should use [Primer](https://github.com/primer/css) in the future. | non_priority | change css to primer proposed changes since the project is mainly design to look like a github page we should use in the future | 0 |
121,029 | 17,644,551,853 | IssuesEvent | 2021-08-20 02:44:46 | Killy85/game_ai_trainer | https://api.github.com/repos/Killy85/game_ai_trainer | opened | CVE-2021-29555 (Medium) detected in tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl | security vulnerability | ## CVE-2021-29555 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learni... | True | CVE-2021-29555 (Medium) detected in tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl - ## CVE-2021-29555 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.13.1-cp27-cp27... | non_priority | cve medium detected in tensorflow whl cve medium severity vulnerability vulnerable library tensorflow whl tensorflow is an open source machine learning framework for everyone library home page a href dependency hierarchy x tensorflow ... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.