Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 7 112 | repo_url stringlengths 36 141 | action stringclasses 3
values | title stringlengths 1 744 | labels stringlengths 4 574 | body stringlengths 9 211k | index stringclasses 10
values | text_combine stringlengths 96 211k | label stringclasses 2
values | text stringlengths 96 188k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
21,435 | 3,508,924,060 | IssuesEvent | 2016-01-08 20:08:23 | aleph7/Upsurge | https://api.github.com/repos/aleph7/Upsurge | closed | LinearType should be a SequenceType | t1: defect | There should be a test case for iterating through elements:
```swift
let elements: LinearType = RealArray([0, 1, 2, 3])
for (index, element) in elements.enumerate() {
XCTAssertEqual(index, element)
}
``` | 1.0 | LinearType should be a SequenceType - There should be a test case for iterating through elements:
```swift
let elements: LinearType = RealArray([0, 1, 2, 3])
for (index, element) in elements.enumerate() {
XCTAssertEqual(index, element)
}
``` | non_process | lineartype should be a sequencetype there should be a test case for iterating through elements swift let elements lineartype realarray for index element in elements enumerate xctassertequal index element | 0 |
690,054 | 23,644,410,986 | IssuesEvent | 2022-08-25 20:24:31 | WarwickAI/wai-platform-v2 | https://api.github.com/repos/WarwickAI/wai-platform-v2 | closed | Add date field to events | enhancement high-priority | For Tutorials and Talks, this will be the date of the event.
For Courses and Project, this will be the starting date of the event.
Can be shown in the `extraInfo` section on the cards, and beneath the heading on the page. | 1.0 | Add date field to events - For Tutorials and Talks, this will be the date of the event.
For Courses and Project, this will be the starting date of the event.
Can be shown in the `extraInfo` section on the cards, and beneath the heading on the page. | non_process | add date field to events for tutorials and talks this will be the date of the event for courses and project this will be the starting date of the event can be shown in the extrainfo section on the cards and beneath the heading on the page | 0 |
30,908 | 4,668,582,161 | IssuesEvent | 2016-10-06 03:24:05 | kubernetes/kubernetes | https://api.github.com/repos/kubernetes/kubernetes | opened | kubernetes-e2e-gci-gce-alpha-features-release-1.4: broken test run | kind/flake priority/P2 team/test-infra | Failed: https://k8s-gubernator.appspot.com/build/kubernetes-jenkins/logs/kubernetes-e2e-gci-gce-alpha-features-release-1.4/-1/
Run so broken it didn't make JUnit output! | 1.0 | kubernetes-e2e-gci-gce-alpha-features-release-1.4: broken test run - Failed: https://k8s-gubernator.appspot.com/build/kubernetes-jenkins/logs/kubernetes-e2e-gci-gce-alpha-features-release-1.4/-1/
Run so broken it didn't make JUnit output! | non_process | kubernetes gci gce alpha features release broken test run failed run so broken it didn t make junit output | 0 |
16,322 | 20,976,637,976 | IssuesEvent | 2022-03-28 15:45:53 | Automattic/woocommerce-payments | https://api.github.com/repos/Automattic/woocommerce-payments | closed | Documents view: document download | category: projects component: invoices for processing fees | ### Description
<!-- A clear and concise description of what the new feature or improvement is. -->
As part of the VAT invoices for processing fees project, merchants should be able to download any documents they see on the Documents list.
### Acceptance criteria
<!-- A list of predefined requirements that must... | 1.0 | Documents view: document download - ### Description
<!-- A clear and concise description of what the new feature or improvement is. -->
As part of the VAT invoices for processing fees project, merchants should be able to download any documents they see on the Documents list.
### Acceptance criteria
<!-- A list ... | process | documents view document download description as part of the vat invoices for processing fees project merchants should be able to download any documents they see on the documents list acceptance criteria clicking the download button in the documents list downloads the document from wcpay s ... | 1 |
62,705 | 15,343,148,402 | IssuesEvent | 2021-02-27 19:04:31 | nunit/nunit-console | https://api.github.com/repos/nunit/nunit-console | closed | Implement Package tests for engine and console runner | is:build pri:high | This will initially be a set of tests implemented in the cake script itself. Since the script is c#, we can port to a test assembly later if we want to test more deeply. However, I've been testing this way in three or four projects and haven't seen any big limitations so far. | 1.0 | Implement Package tests for engine and console runner - This will initially be a set of tests implemented in the cake script itself. Since the script is c#, we can port to a test assembly later if we want to test more deeply. However, I've been testing this way in three or four projects and haven't seen any big limitat... | non_process | implement package tests for engine and console runner this will initially be a set of tests implemented in the cake script itself since the script is c we can port to a test assembly later if we want to test more deeply however i ve been testing this way in three or four projects and haven t seen any big limitat... | 0 |
211,435 | 23,825,600,641 | IssuesEvent | 2022-09-05 14:37:35 | sast-automation-dev/soundcloud-redux-11 | https://api.github.com/repos/sast-automation-dev/soundcloud-redux-11 | opened | react-scripts-1.0.10.tgz: 77 vulnerabilities (highest severity is: 10.0) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>react-scripts-1.0.10.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/sast-autom... | True | react-scripts-1.0.10.tgz: 77 vulnerabilities (highest severity is: 10.0) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>react-scripts-1.0.10.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.jso... | non_process | react scripts tgz vulnerabilities highest severity is vulnerable library react scripts tgz path to dependency file package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available ... | 0 |
21,971 | 30,464,658,255 | IssuesEvent | 2023-07-17 09:30:28 | MicrosoftDocs/azure-devops-docs | https://api.github.com/repos/MicrosoftDocs/azure-devops-docs | closed | Typo: "...and works out its way." should be "...and works its way out." | doc-bug Pri1 azure-devops-pipelines/svc azure-devops-pipelines-process/subsvc |
[Enter feedback here]
---
#### Document Details
⚠ *Do not edit this section. It is required for learn.microsoft.com ➟ GitHub issue linking.*
* ID: 21e5cee4-eaae-3a96-db91-540ac759e83a
* Version Independent ID: 9bdc837c-ffe0-d999-f922-f3a5debc7f92
* Content: [Conditions - Azure Pipelines](https://learn.m... | 1.0 | Typo: "...and works out its way." should be "...and works its way out." -
[Enter feedback here]
---
#### Document Details
⚠ *Do not edit this section. It is required for learn.microsoft.com ➟ GitHub issue linking.*
* ID: 21e5cee4-eaae-3a96-db91-540ac759e83a
* Version Independent ID: 9bdc837c-ffe0-d999-... | process | typo and works out its way should be and works its way out document details ⚠ do not edit this section it is required for learn microsoft com ➟ github issue linking id eaae version independent id content content source service ... | 1 |
4,871 | 7,753,030,038 | IssuesEvent | 2018-05-30 22:27:02 | GoogleCloudPlatform/google-cloud-python | https://api.github.com/repos/GoogleCloudPlatform/google-cloud-python | closed | BigQuery 1.2.0 release | api: bigquery packaging type: process | The big new feature is https://github.com/GoogleCloudPlatform/google-cloud-python/pull/5267 which adds support for column-based time partitioning. | 1.0 | BigQuery 1.2.0 release - The big new feature is https://github.com/GoogleCloudPlatform/google-cloud-python/pull/5267 which adds support for column-based time partitioning. | process | bigquery release the big new feature is which adds support for column based time partitioning | 1 |
29 | 2,497,604,967 | IssuesEvent | 2015-01-07 09:07:59 | sysown/proxysql-0.2 | https://api.github.com/repos/sysown/proxysql-0.2 | closed | implement query processing in Standard_Query_Processor::process_mysql_query() | bug development QUERY PROCESSOR | It seems that right now only regex matching is enabled.
username, schemaname, flagIN/flagOUT and apply are still not implemented.
Query rewrite (replace_pattern) is not implemented either. | 1.0 | implement query processing in Standard_Query_Processor::process_mysql_query() - It seems that right now only regex matching is enabled.
username, schemaname, flagIN/flagOUT and apply are still not implemented.
Query rewrite (replace_pattern) is not implemented either. | process | implement query processing in standard query processor process mysql query it seems that right now only regex matching is enabled username schemaname flagin flagout and apply are still not implemented query rewrite replace pattern is not implemented either | 1 |
1,823 | 4,581,159,709 | IssuesEvent | 2016-09-19 02:52:29 | VietOpenCPS/opencps | https://api.github.com/repos/VietOpenCPS/opencps | closed | Hiển thị dịch vụ công chưa được gán quy trình xử lý trên màn hình tạo mới hồ sơ | bug service_process | 1. Đăng nhập tài khoản doanh nghiệp
2. Vào quản lý hồ sơ, nhấn nút Tạo mới hồ sơ
Lỗi: Hiển thị dịch vụ công chưa được gán quy trình xử lý trên màn hình tạo mới hồ sơ | 1.0 | Hiển thị dịch vụ công chưa được gán quy trình xử lý trên màn hình tạo mới hồ sơ - 1. Đăng nhập tài khoản doanh nghiệp
2. Vào quản lý hồ sơ, nhấn nút Tạo mới hồ sơ
Lỗi: Hiển thị dịch vụ công chưa được gán quy trình xử lý trên màn hình tạo mới hồ sơ | process | hiển thị dịch vụ công chưa được gán quy trình xử lý trên màn hình tạo mới hồ sơ đăng nhập tài khoản doanh nghiệp vào quản lý hồ sơ nhấn nút tạo mới hồ sơ lỗi hiển thị dịch vụ công chưa được gán quy trình xử lý trên màn hình tạo mới hồ sơ | 1 |
20,266 | 26,889,164,214 | IssuesEvent | 2023-02-06 07:21:48 | qgis/QGIS | https://api.github.com/repos/qgis/QGIS | closed | Area Simplify drops Z and M values | Processing Bug | ### What is the bug or the crash?
If you run the Simplify Algo with Area(Visvalingam) the Z and M values will become null if any vertexes are removed.
### Steps to reproduce the issue
1. Create a line layer with Z at 100 and M values set and enough vertices to be able to run simplify.
2. Run the simplify algo... | 1.0 | Area Simplify drops Z and M values - ### What is the bug or the crash?
If you run the Simplify Algo with Area(Visvalingam) the Z and M values will become null if any vertexes are removed.
### Steps to reproduce the issue
1. Create a line layer with Z at 100 and M values set and enough vertices to be able to run... | process | area simplify drops z and m values what is the bug or the crash if you run the simplify algo with area visvalingam the z and m values will become null if any vertexes are removed steps to reproduce the issue create a line layer with z at and m values set and enough vertices to be able to run s... | 1 |
35,692 | 9,645,533,883 | IssuesEvent | 2019-05-17 08:54:50 | yandex/ClickHouse | https://api.github.com/repos/yandex/ClickHouse | opened | build failed, by clang 8.0.0 | build | hi, Thank you for your work.
I compiled in stable version (19.5.3.8 stable) wrong.
first, Download the code from LLVM and copy the code from the driver directory to compiler_8.0.0 and compiler_8.0.0svn.
second, The build code.
failed message:
CMake Error at dbms/programs/clang/Compiler-8.0.0svn/CMakeLists.txt:32... | 1.0 | build failed, by clang 8.0.0 - hi, Thank you for your work.
I compiled in stable version (19.5.3.8 stable) wrong.
first, Download the code from LLVM and copy the code from the driver directory to compiler_8.0.0 and compiler_8.0.0svn.
second, The build code.
failed message:
CMake Error at dbms/programs/clang/Comp... | non_process | build failed by clang hi thank you for your work i compiled in stable version stable wrong first download the code from llvm and copy the code from the driver directory to compiler and compiler second the build code failed message cmake error at dbms programs clang compiler... | 0 |
4,235 | 7,186,868,053 | IssuesEvent | 2018-02-02 01:33:03 | Great-Hill-Corporation/quickBlocks | https://api.github.com/repos/Great-Hill-Corporation/quickBlocks | closed | Transactions may fail without sending "out of gas". Internal calls does not use gas in parent (maybe) | monitors-all status-inprocess type-bug | An internal call in this transaction (0xd20a95a9f051d6961ca766a9b2d0f18b6afdf6d8465931a3f70f2c4b1c023688) ran out of gas, but this transaction did not run out of gas, so I don't identify them as inError. The gas!=gasUsed, therefore, I don't trace it. | 1.0 | Transactions may fail without sending "out of gas". Internal calls does not use gas in parent (maybe) - An internal call in this transaction (0xd20a95a9f051d6961ca766a9b2d0f18b6afdf6d8465931a3f70f2c4b1c023688) ran out of gas, but this transaction did not run out of gas, so I don't identify them as inError. The gas!=gas... | process | transactions may fail without sending out of gas internal calls does not use gas in parent maybe an internal call in this transaction ran out of gas but this transaction did not run out of gas so i don t identify them as inerror the gas gasused therefore i don t trace it | 1 |
71,670 | 7,254,797,535 | IssuesEvent | 2018-02-16 12:31:42 | edenlabllc/ehealth.api | https://api.github.com/repos/edenlabllc/ehealth.api | closed | Cancelled declaration_request with person w/o tax_id | epic/declaration kind/bug kind/support status/test | original request https://github.com/ehealth-ua/api-spec/issues/213
## Steps to Reproduce (Repro steps)
- [ ] POST https://api.ehealth.world/api/declaration_requests
- [ ] Створюємо декл.реквест для користувача без ІПН 63a3128c-cbbf-4398-a5ba-2598cf83f80e , не підтверджуємо його і потім зразу ж створюємо для іншого та... | 1.0 | Cancelled declaration_request with person w/o tax_id - original request https://github.com/ehealth-ua/api-spec/issues/213
## Steps to Reproduce (Repro steps)
- [ ] POST https://api.ehealth.world/api/declaration_requests
- [ ] Створюємо декл.реквест для користувача без ІПН 63a3128c-cbbf-4398-a5ba-2598cf83f80e , не під... | non_process | cancelled declaration request with person w o tax id original request steps to reproduce repro steps post створюємо декл реквест для користувача без іпн cbbf не підтверджуємо його і потім зразу ж створюємо для іншого також без іпн у них різні піб дати народження і стать в рез... | 0 |
38,778 | 15,793,582,500 | IssuesEvent | 2021-04-02 09:16:17 | AutoPacker-OSS/autopacker | https://api.github.com/repos/AutoPacker-OSS/autopacker | opened | "undefined Projects" when organization has no projects | Priority: Low Service: Web App Status: Pending Type: Bug | When an organization has no projects, its dashboard shows a wrong message:

Should say "No projects", or something like that. No "undefined" | 1.0 | "undefined Projects" when organization has no projects - When an organization has no projects, its dashboard shows a wrong message:

Should say "No projects", or something like that. No "undefined" | non_process | undefined projects when organization has no projects when an organization has no projects its dashboard shows a wrong message should say no projects or something like that no undefined | 0 |
88,777 | 17,663,608,706 | IssuesEvent | 2021-08-22 02:12:31 | adventuregamestudio/ags | https://api.github.com/repos/adventuregamestudio/ags | closed | INFO: a variant of utf8 support for translations | type: information context: unicode | A while ago @mgambrell has pointed me his work on hacking in utf-8 string support for translations. It's based on modifying alfont source to use parts of the **musl** library to convert strings.
Here's the commit (and maybe there are more commits around): https://github.com/RatalaikaGames/ags/commit/a00e7d933458d836... | 1.0 | INFO: a variant of utf8 support for translations - A while ago @mgambrell has pointed me his work on hacking in utf-8 string support for translations. It's based on modifying alfont source to use parts of the **musl** library to convert strings.
Here's the commit (and maybe there are more commits around): https://gi... | non_process | info a variant of support for translations a while ago mgambrell has pointed me his work on hacking in utf string support for translations it s based on modifying alfont source to use parts of the musl library to convert strings here s the commit and maybe there are more commits around i am lea... | 0 |
5,822 | 8,657,197,579 | IssuesEvent | 2018-11-27 20:36:28 | brucemiller/LaTeXML | https://api.github.com/repos/brucemiller/LaTeXML | closed | Page break compatibility? | enhancement postprocessing | Hi there, this is a great program!
In case the authors are not aware, LaTeXML can also be used as part of the process to produce ebooks! Since it produces HTML, it is just a matter of converting the HTML into EPUB or other format using tools like Calibre.
Anyway, my question relates to commands like `\pagebreak`... | 1.0 | Page break compatibility? - Hi there, this is a great program!
In case the authors are not aware, LaTeXML can also be used as part of the process to produce ebooks! Since it produces HTML, it is just a matter of converting the HTML into EPUB or other format using tools like Calibre.
Anyway, my question relates t... | process | page break compatibility hi there this is a great program in case the authors are not aware latexml can also be used as part of the process to produce ebooks since it produces html it is just a matter of converting the html into epub or other format using tools like calibre anyway my question relates t... | 1 |
17,342 | 23,165,852,310 | IssuesEvent | 2022-07-30 00:57:46 | hashgraph/hedera-json-rpc-relay | https://api.github.com/repos/hashgraph/hedera-json-rpc-relay | closed | Add consensus node calling endpoints to postman tests | enhancement P2 process | ### Problem
Currently the postman tests are missing calls that query the consensus nodes.
This would be useful in quick sanity checks to verify relay operation as they do not require knowledge of accounts and blocks details
### Solution
Add consensus node calling checks
- `eth_gasPrice`
- `eth_feeHistory` - use ... | 1.0 | Add consensus node calling endpoints to postman tests - ### Problem
Currently the postman tests are missing calls that query the consensus nodes.
This would be useful in quick sanity checks to verify relay operation as they do not require knowledge of accounts and blocks details
### Solution
Add consensus node cal... | process | add consensus node calling endpoints to postman tests problem currently the postman tests are missing calls that query the consensus nodes this would be useful in quick sanity checks to verify relay operation as they do not require knowledge of accounts and blocks details solution add consensus node cal... | 1 |
13,681 | 2,775,782,979 | IssuesEvent | 2015-05-04 18:03:27 | douglasdrumond/macvim | https://api.github.com/repos/douglasdrumond/macvim | closed | Auto-constraints warning under Yosemite | auto-migrated Priority-Medium Type-Defect | ```
Got this error when running MacVim under Yosemite:
Unable to simultaneously satisfy constraints:
(
"<NSAutoresizingMaskLayoutConstraint:0x7fe499dcde70 h=--& v=--& V:[FI_TBrowserBackgroundView:0x7fe49c5793a0(0)]>",
"<NSAutoresizingMaskLayoutConstraint:0x7fe49c4146e0 h=-&- v=-&- V:|-(0)-[FI_TListScrollView:0... | 1.0 | Auto-constraints warning under Yosemite - ```
Got this error when running MacVim under Yosemite:
Unable to simultaneously satisfy constraints:
(
"<NSAutoresizingMaskLayoutConstraint:0x7fe499dcde70 h=--& v=--& V:[FI_TBrowserBackgroundView:0x7fe49c5793a0(0)]>",
"<NSAutoresizingMaskLayoutConstraint:0x7fe49c4146e... | non_process | auto constraints warning under yosemite got this error when running macvim under yosemite unable to simultaneously satisfy constraints will attempt to recover by breaking constraint nsautoresizingmasklayoutconstraint h v v ... | 0 |
22,105 | 30,635,736,103 | IssuesEvent | 2023-07-24 17:36:32 | metabase/metabase | https://api.github.com/repos/metabase/metabase | closed | [MLv2] [Bug] Column name calculation is wrong for columns in `:breakout` from joins | Type:Bug .Backend .metabase-lib .Team/QueryProcessor :hammer_and_wrench: | Note: uses new mock metadata from #29906
Failing test:
```clj
(deftest ^:parallel metadata-for-join-in-previous-stage-test
(let [query {:lib/type :mbql/query
:lib/metadata meta/metadata-provider
:database (meta/id)
:type :pipeline
... | 1.0 | [MLv2] [Bug] Column name calculation is wrong for columns in `:breakout` from joins - Note: uses new mock metadata from #29906
Failing test:
```clj
(deftest ^:parallel metadata-for-join-in-previous-stage-test
(let [query {:lib/type :mbql/query
:lib/metadata meta/metadata-provider
... | process | column name calculation is wrong for columns in breakout from joins note uses new mock metadata from failing test clj deftest parallel metadata for join in previous stage test let query lib type mbql query lib metadata meta metadata provider datab... | 1 |
18,676 | 24,594,078,527 | IssuesEvent | 2022-10-14 06:40:06 | GoogleCloudPlatform/fda-mystudies | https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies | closed | [FHIR] FHIR viewer > Questionnaire > 'Spatial span memory' activity is not getting displayed | Bug P0 Response datastore Process: Fixed Process: Tested dev | **Pre-condition:** Add 'Spatial span memory' activity in the study builder and publish the study
**AR:** FHIR viewer > Questionnaire > Spatial span memory activity is not getting displayed
**ER:** FHIR viewer > Questionnaire > Spatial span memory activity should get displayed | 2.0 | [FHIR] FHIR viewer > Questionnaire > 'Spatial span memory' activity is not getting displayed - **Pre-condition:** Add 'Spatial span memory' activity in the study builder and publish the study
**AR:** FHIR viewer > Questionnaire > Spatial span memory activity is not getting displayed
**ER:** FHIR viewer > Question... | process | fhir viewer questionnaire spatial span memory activity is not getting displayed pre condition add spatial span memory activity in the study builder and publish the study ar fhir viewer questionnaire spatial span memory activity is not getting displayed er fhir viewer questionnaire... | 1 |
16,485 | 21,443,608,013 | IssuesEvent | 2022-04-25 02:12:06 | huutho77/CNPMNC_ThayAi | https://api.github.com/repos/huutho77/CNPMNC_ThayAi | opened | [API] Coding feature filter products based on Category | dev/thnguyen processing | - Parameters need to be input:
- [ ] categoryID
- Output expect:
- [ ] Products list related has been found | 1.0 | [API] Coding feature filter products based on Category - - Parameters need to be input:
- [ ] categoryID
- Output expect:
- [ ] Products list related has been found | process | coding feature filter products based on category parameters need to be input categoryid output expect products list related has been found | 1 |
17,681 | 23,515,865,320 | IssuesEvent | 2022-08-18 21:17:26 | open-telemetry/opentelemetry-collector-contrib | https://api.github.com/repos/open-telemetry/opentelemetry-collector-contrib | closed | [processor/metricstransform] aggregate_labels inconsistent results | bug priority:p2 data:metrics processor/metricstransform | **Describe the bug**
Trying to aggregate a histogram using metricstransform (aggregate_labels) produce inconsistent results.
**Steps to reproduce**
Use a prometheus recivier to scrape a histogram that have multiple values like this:
<details><summary>METRICS</summary>
<p>
```
# HELP Response_Time Opera... | 1.0 | [processor/metricstransform] aggregate_labels inconsistent results - **Describe the bug**
Trying to aggregate a histogram using metricstransform (aggregate_labels) produce inconsistent results.
**Steps to reproduce**
Use a prometheus recivier to scrape a histogram that have multiple values like this:
<detai... | process | aggregate labels inconsistent results describe the bug trying to aggregate a histogram using metricstransform aggregate labels produce inconsistent results steps to reproduce use a prometheus recivier to scrape a histogram that have multiple values like this metrics help resp... | 1 |
2,672 | 5,476,133,327 | IssuesEvent | 2017-03-11 17:53:51 | paulkornikov/Pragonas | https://api.github.com/repos/paulkornikov/Pragonas | closed | Fonction d'export des opés déductibles impôts | a-enhancement processus workload V | Filtrer les opérations déductibles puis produire le csv.
Sauvegarder le csv sur le serveur.
Mettre la location de mapping dans le XML de config. | 1.0 | Fonction d'export des opés déductibles impôts - Filtrer les opérations déductibles puis produire le csv.
Sauvegarder le csv sur le serveur.
Mettre la location de mapping dans le XML de config. | process | fonction d export des opés déductibles impôts filtrer les opérations déductibles puis produire le csv sauvegarder le csv sur le serveur mettre la location de mapping dans le xml de config | 1 |
16,863 | 22,143,037,764 | IssuesEvent | 2022-06-03 08:58:05 | camunda/zeebe | https://api.github.com/repos/camunda/zeebe | closed | [EPIC] Refactor Elasticsearch Exporter Tests | kind/toil scope/broker kind/epic team/process-automation area/test | **Description**
The `elasticsearch-exporter` integration tests are currently quite convoluted. Historically, the `elasticsearch-exporter` tests used to depend on `zeebe-test` which was removed in https://github.com/camunda-cloud/zeebe/pull/8608. During the removal, some of the `zeebe-test` utilities ended up in the ... | 1.0 | [EPIC] Refactor Elasticsearch Exporter Tests - **Description**
The `elasticsearch-exporter` integration tests are currently quite convoluted. Historically, the `elasticsearch-exporter` tests used to depend on `zeebe-test` which was removed in https://github.com/camunda-cloud/zeebe/pull/8608. During the removal, some... | process | refactor elasticsearch exporter tests description the elasticsearch exporter integration tests are currently quite convoluted historically the elasticsearch exporter tests used to depend on zeebe test which was removed in during the removal some of the zeebe test utilities ended up in the elast... | 1 |
220,688 | 17,227,450,969 | IssuesEvent | 2021-07-20 05:18:15 | WordPress/gutenberg | https://api.github.com/repos/WordPress/gutenberg | closed | Dashicon improperly aligned in ToolbarButton without label | Needs Testing [Feature] UI Components | ## Description
Since 5.7-RC3 a dashicon in ToolbarButton without any label text has right margin. This wasn't the case before and is also different from how a svg icon works.
## Screenshots or screen recording (optional)

, etc.
| 1.0 | Rework "INSTALL.md" - ### Issue
Since the upcoming 2.5 branch of SMW breaks compatibility with versions of MediaWiki 1.23.0 and lower the "INSTALL.md" should be reworked as it makes a lot of now unnecessary references to earlier versions and does not at all mention the worries introduced by MediaWiki 1.25+ ("composer.... | non_process | rework install md issue since the upcoming branch of smw breaks compatibility with versions of mediawiki and lower the install md should be reworked as it makes a lot of now unnecessary references to earlier versions and does not at all mention the worries introduced by mediawiki composer lo... | 0 |
9,635 | 12,599,661,592 | IssuesEvent | 2020-06-11 06:34:25 | allinurl/goaccess | https://api.github.com/repos/allinurl/goaccess | closed | How to seperate those statistics data by http domain(host)? | log-processing question | As the title mentioned, how can i classify the result by the http domain, for example, the top N requests data? | 1.0 | How to seperate those statistics data by http domain(host)? - As the title mentioned, how can i classify the result by the http domain, for example, the top N requests data? | process | how to seperate those statistics data by http domain host as the title mentioned how can i classify the result by the http domain for example the top n requests data | 1 |
16,593 | 21,642,161,485 | IssuesEvent | 2022-05-05 20:01:28 | googleapis/google-cloud-ruby | https://api.github.com/repos/googleapis/google-cloud-ruby | closed | Warning: a recent release failed | type: process | The following release PRs may have failed:
* #18200
* #18201
* #18202
* #18204
* #18205 | 1.0 | Warning: a recent release failed - The following release PRs may have failed:
* #18200
* #18201
* #18202
* #18204
* #18205 | process | warning a recent release failed the following release prs may have failed | 1 |
262,938 | 27,989,538,833 | IssuesEvent | 2023-03-27 01:40:18 | Killy85/game_ai_trainer | https://api.github.com/repos/Killy85/game_ai_trainer | opened | CVE-2023-25666 (High) detected in tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl | Mend: dependency security vulnerability | ## CVE-2023-25666 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning... | True | CVE-2023-25666 (High) detected in tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl - ## CVE-2023-25666 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.13.1-cp27-cp27mu-m... | non_process | cve high detected in tensorflow whl cve high severity vulnerability vulnerable library tensorflow whl tensorflow is an open source machine learning framework for everyone library home page a href dependency hierarchy x tensorflow ... | 0 |
22,450 | 31,169,299,065 | IssuesEvent | 2023-08-16 22:56:41 | googleapis/gapic-generator-python | https://api.github.com/repos/googleapis/gapic-generator-python | closed | Add service YAML files to the golden integration tests | type: process | All of the golden files are missing the service YAML config files except [eventarc](https://github.com/googleapis/gapic-generator-python/blob/main/tests/integration/eventarc_v1.yaml). We should add/update these files to improve our integration testing. | 1.0 | Add service YAML files to the golden integration tests - All of the golden files are missing the service YAML config files except [eventarc](https://github.com/googleapis/gapic-generator-python/blob/main/tests/integration/eventarc_v1.yaml). We should add/update these files to improve our integration testing. | process | add service yaml files to the golden integration tests all of the golden files are missing the service yaml config files except we should add update these files to improve our integration testing | 1 |
67,880 | 14,891,996,988 | IssuesEvent | 2021-01-21 01:46:48 | phytomichael/KSA | https://api.github.com/repos/phytomichael/KSA | opened | CVE-2020-36180 (Medium) detected in jackson-databind-2.8.1.jar | security vulnerability | ## CVE-2020-36180 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.1.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core stream... | True | CVE-2020-36180 (Medium) detected in jackson-databind-2.8.1.jar - ## CVE-2020-36180 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.1.jar</b></p></summary>
<p>Gen... | non_process | cve medium detected in jackson databind jar cve medium severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file ksa ksa ksa ksa service ro... | 0 |
26,259 | 2,684,274,314 | IssuesEvent | 2015-03-28 20:35:34 | ConEmu/old-issues | https://api.github.com/repos/ConEmu/old-issues | closed | Crash whilst resizing Conemu window | 2–5 stars bug duplicate imported Priority-Medium | _From [col.brad...@gmail.com](https://code.google.com/u/103901031233724257395/) on January 24, 2013 00:00:36_
Required information! OS version: Win2k/WinXP/Vista/Win7/Win8 SP? x86/x64 ConEmu version: ? Far version (if you are using Far Manager): ? *Bug description* Conemu crashes whilst resizing window. *Steps to ... | 1.0 | Crash whilst resizing Conemu window - _From [col.brad...@gmail.com](https://code.google.com/u/103901031233724257395/) on January 24, 2013 00:00:36_
Required information! OS version: Win2k/WinXP/Vista/Win7/Win8 SP? x86/x64 ConEmu version: ? Far version (if you are using Far Manager): ? *Bug description* Conemu cras... | non_process | crash whilst resizing conemu window from on january required information os version winxp vista sp conemu version far version if you are using far manager bug description conemu crashes whilst resizing window steps to reproduction open single instance of conemu ... | 0 |
6,783 | 9,917,114,974 | IssuesEvent | 2019-06-28 22:29:46 | HumanCellAtlas/dcp-community | https://api.github.com/repos/HumanCellAtlas/dcp-community | closed | Improving community notifications for charters | charter-process | - [ ] Use #dcp-announce[ments] instead of #dcp channel for charter _state changes_ | 1.0 | Improving community notifications for charters - - [ ] Use #dcp-announce[ments] instead of #dcp channel for charter _state changes_ | process | improving community notifications for charters use dcp announce instead of dcp channel for charter state changes | 1 |
14,027 | 16,826,829,384 | IssuesEvent | 2021-06-17 19:49:18 | hashgraph/hedera-mirror-node | https://api.github.com/repos/hashgraph/hedera-mirror-node | opened | Rename master branch to main | P1 enhancement process | **Problem**
In honor of [Juneteenth](https://en.wikipedia.org/wiki/Juneteenth), we want to rename our master branch to main as much of the industry already has.
**Solution**
- Change any references to master in the codebase to `main`
- Rename master branch to main in Github settings
- Adjust local git settings
... | 1.0 | Rename master branch to main - **Problem**
In honor of [Juneteenth](https://en.wikipedia.org/wiki/Juneteenth), we want to rename our master branch to main as much of the industry already has.
**Solution**
- Change any references to master in the codebase to `main`
- Rename master branch to main in Github settings... | process | rename master branch to main problem in honor of we want to rename our master branch to main as much of the industry already has solution change any references to master in the codebase to main rename master branch to main in github settings adjust local git settings shell git branc... | 1 |
77,556 | 27,049,323,444 | IssuesEvent | 2023-02-13 12:07:52 | notofonts/telugu | https://api.github.com/repos/notofonts/telugu | closed | The base line for noto sans Telugu is not in line with English and punctuation marks. | Type-Defect Script-Telugu Android FoundIn-1.x in-evaluation | ```
What steps will reproduce the problem?
1.Typing in Telugu make the baseline higher compared to English or hindi
2.The same happens for kannada too
3.
What is the expected output? What do you see instead?
The base line of Telugu and kannada are supposed to be in line with English and
hindi in order to use punctua... | 1.0 | The base line for noto sans Telugu is not in line with English and punctuation marks. - ```
What steps will reproduce the problem?
1.Typing in Telugu make the baseline higher compared to English or hindi
2.The same happens for kannada too
3.
What is the expected output? What do you see instead?
The base line of Telu... | non_process | the base line for noto sans telugu is not in line with english and punctuation marks what steps will reproduce the problem typing in telugu make the baseline higher compared to english or hindi the same happens for kannada too what is the expected output what do you see instead the base line of telu... | 0 |
6,072 | 8,909,442,947 | IssuesEvent | 2019-01-18 06:18:19 | mick-warehime/sixth_corp | https://api.github.com/repos/mick-warehime/sixth_corp | closed | remove union in factory constructors | development process | if isinstance(character, CharacterTypes):
data = character.data
else:
data = character | 1.0 | remove union in factory constructors - if isinstance(character, CharacterTypes):
data = character.data
else:
data = character | process | remove union in factory constructors if isinstance character charactertypes data character data else data character | 1 |
697,787 | 23,952,758,278 | IssuesEvent | 2022-09-12 12:53:06 | epicmaxco/vuestic-ui | https://api.github.com/repos/epicmaxco/vuestic-ui | opened | On dark theme sponsors are not very visible. | BUG good first issue LOW PRIORITY difficulty: I'm too young to die | 
Probably just needs an opaque white background for existing images, but you can investigate a bit.
Might be possible to do in context of markdown, github allowed some html before. | 1.0 | On dark theme sponsors are not very visible. - 
Probably just needs an opaque white background for existing images, but you can investigate a bit.
Might be possible to do in context of markdown, github al... | non_process | on dark theme sponsors are not very visible probably just needs an opaque white background for existing images but you can investigate a bit might be possible to do in context of markdown github allowed some html before | 0 |
362,436 | 10,727,523,395 | IssuesEvent | 2019-10-28 11:55:16 | ISISScientificComputing/autoreduce | https://api.github.com/repos/ISISScientificComputing/autoreduce | closed | Refactor Hot Fixes from Python 3 Compatibility Upgrade | 🔑 Internal 🕐 Low priority | Issue raised by: [developer]
### What?
Many changes were made to the Autoreduction codebase to fix any incompatibilities when upgrading to Python 3 before end of life.
We should go back to create more permanent fixes for these changes where applicable to maintain a clean and readable codebase.
### Where?
1.... | 1.0 | Refactor Hot Fixes from Python 3 Compatibility Upgrade - Issue raised by: [developer]
### What?
Many changes were made to the Autoreduction codebase to fix any incompatibilities when upgrading to Python 3 before end of life.
We should go back to create more permanent fixes for these changes where applicable to ... | non_process | refactor hot fixes from python compatibility upgrade issue raised by what many changes were made to the autoreduction codebase to fix any incompatibilities when upgrading to python before end of life we should go back to create more permanent fixes for these changes where applicable to maintain a... | 0 |
16,502 | 2,906,427,067 | IssuesEvent | 2015-06-19 09:58:10 | cakephp/cakephp | https://api.github.com/repos/cakephp/cakephp | closed | 3.x PaginatorComponent defect | Defect |
If this is sortWhitelist: `sortWhitelist => []`,
and this is the url: `/controller/action?sort=field`.
The PaginatorComponent will sort by that field, ignoring that we don't want to allow sorting any field.
Instead of empty sortWhitelist, if the sortWhitelist isn't empty like this: `sortWhitelist => ['even_inval... | 1.0 | 3.x PaginatorComponent defect -
If this is sortWhitelist: `sortWhitelist => []`,
and this is the url: `/controller/action?sort=field`.
The PaginatorComponent will sort by that field, ignoring that we don't want to allow sorting any field.
Instead of empty sortWhitelist, if the sortWhitelist isn't empty like this... | non_process | x paginatorcomponent defect if this is sortwhitelist sortwhitelist and this is the url controller action sort field the paginatorcomponent will sort by that field ignoring that we don t want to allow sorting any field instead of empty sortwhitelist if the sortwhitelist isn t empty like this ... | 0 |
20,263 | 26,883,300,588 | IssuesEvent | 2023-02-05 22:07:57 | km4ack/pi-build | https://api.github.com/repos/km4ack/pi-build | closed | QSSTV Site Down | bug Slated in process | The [site](http://users.telenet.be/on4qz/qsstv/downloads/) where BAP downloads QSSTV is down. Thanks Bruce, W1BAW, for catching the issue. | 1.0 | QSSTV Site Down - The [site](http://users.telenet.be/on4qz/qsstv/downloads/) where BAP downloads QSSTV is down. Thanks Bruce, W1BAW, for catching the issue. | process | qsstv site down the where bap downloads qsstv is down thanks bruce for catching the issue | 1 |
8,458 | 11,631,219,684 | IssuesEvent | 2020-02-28 00:39:44 | geneontology/go-ontology | https://api.github.com/repos/geneontology/go-ontology | closed | regulation of mitotic DNA replication initiation from early origin | New term request PomBase cell cycle and DNA processes | by analogy with GO:0101017; for S. pombe rik1 and some phenotype LDs
id: GO:new
name: regulation of mitotic DNA replication initiation from early origin
namespace: biological_process
def: "Any process that modulates the frequency, rate or extent of firing from an early origin of replication involved in mitotic DN... | 1.0 | regulation of mitotic DNA replication initiation from early origin - by analogy with GO:0101017; for S. pombe rik1 and some phenotype LDs
id: GO:new
name: regulation of mitotic DNA replication initiation from early origin
namespace: biological_process
def: "Any process that modulates the frequency, rate or extent... | process | regulation of mitotic dna replication initiation from early origin by analogy with go for s pombe and some phenotype lds id go new name regulation of mitotic dna replication initiation from early origin namespace biological process def any process that modulates the frequency rate or extent of firin... | 1 |
19,395 | 25,539,287,645 | IssuesEvent | 2022-11-29 14:16:29 | ESMValGroup/ESMValCore | https://api.github.com/repos/ESMValGroup/ESMValCore | closed | Preprocessor `multimodel_statistics` fails when data have no time dimension | bug preprocessor | **Describe the bug**
Hi all, I'm developing some tests for the multimodel statistics using real data (#856), and I'm coming accross this bug:
Running multimodel statistics with a list of cubes with **no time dimension**, will result in
`ValueError: Cannot guess bounds for a coordinate of length 1.`
The bug can ... | 1.0 | Preprocessor `multimodel_statistics` fails when data have no time dimension - **Describe the bug**
Hi all, I'm developing some tests for the multimodel statistics using real data (#856), and I'm coming accross this bug:
Running multimodel statistics with a list of cubes with **no time dimension**, will result in
`... | process | preprocessor multimodel statistics fails when data have no time dimension describe the bug hi all i m developing some tests for the multimodel statistics using real data and i m coming accross this bug running multimodel statistics with a list of cubes with no time dimension will result in va... | 1 |
9,717 | 12,716,589,366 | IssuesEvent | 2020-06-24 02:24:24 | OUDcollective/twenty20times | https://api.github.com/repos/OUDcollective/twenty20times | opened | Understanding the GitHub flow · GitHub Guides | workflow-process | 
## WHAT IS A PULL REQUEST
***GitHub Guides & Best Practices**
---
**Source URL**:
[https://guides.github.com/introduction/flow/](https://guides.github.... | 1.0 | Understanding the GitHub flow · GitHub Guides - 
## WHAT IS A PULL REQUEST
***GitHub Guides & Best Practices**
---
**Source URL**:
[https://guides.githu... | process | understanding the github flow · github guides what is a pull request github guides best practices source url browser chrome os windows bit screen size viewport size pixel ratio zoom level | 1 |
22,049 | 7,112,351,934 | IssuesEvent | 2018-01-17 16:46:19 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | closed | Build is buggy for java 9. | :Core build | Try compiling with java 9:
First you will hit this. This can be fixed by using `assertEquals`, which also simplifies the test.
```
/home/rmuir/workspace/elasticsearch/core/src/test/java/org/elasticsearch/threadpool/ScalingThreadPoolTests.java:180: error: method invoked with incorrect number of arguments; expected 2, ... | 1.0 | Build is buggy for java 9. - Try compiling with java 9:
First you will hit this. This can be fixed by using `assertEquals`, which also simplifies the test.
```
/home/rmuir/workspace/elasticsearch/core/src/test/java/org/elasticsearch/threadpool/ScalingThreadPoolTests.java:180: error: method invoked with incorrect numb... | non_process | build is buggy for java try compiling with java first you will hit this this can be fixed by using assertequals which also simplifies the test home rmuir workspace elasticsearch core src test java org elasticsearch threadpool scalingthreadpooltests java error method invoked with incorrect number... | 0 |
10,529 | 27,119,221,656 | IssuesEvent | 2023-02-15 21:14:33 | Azure/azure-sdk | https://api.github.com/repos/Azure/azure-sdk | closed | Board Review: Preview Features in Stable Packages | architecture board-review | The Cosmos team is requesting that we support shipping preview features in stable packages. Something like that already shipped in Cosmos Java packages, and the most recent request is for .NET Cosmos packages. We should talk at the arch board level if and how we want to support such requests.
The .NET platform supp... | 1.0 | Board Review: Preview Features in Stable Packages - The Cosmos team is requesting that we support shipping preview features in stable packages. Something like that already shipped in Cosmos Java packages, and the most recent request is for .NET Cosmos packages. We should talk at the arch board level if and how we want ... | non_process | board review preview features in stable packages the cosmos team is requesting that we support shipping preview features in stable packages something like that already shipped in cosmos java packages and the most recent request is for net cosmos packages we should talk at the arch board level if and how we want ... | 0 |
344,896 | 30,771,003,658 | IssuesEvent | 2023-07-30 22:37:45 | dancergraham/e57-python | https://api.github.com/repos/dancergraham/e57-python | closed | Tests: 🐇 bunny reading results | help wanted good first issue test | Test that the extents (max - min coordinates) of the bunny pointcloud are close to
Box dimensions
X: 0.155698
Y: 0.14731
Z: 0.120672
Global box center (median position)
X: -0.016840
Y: 0.113666
Z: -0.001537 | 1.0 | Tests: 🐇 bunny reading results - Test that the extents (max - min coordinates) of the bunny pointcloud are close to
Box dimensions
X: 0.155698
Y: 0.14731
Z: 0.120672
Global box center (median position)
X: -0.016840
Y: 0.113666
Z: -0.001537 | non_process | tests 🐇 bunny reading results test that the extents max min coordinates of the bunny pointcloud are close to box dimensions x y z global box center median position x y z | 0 |
1,096 | 3,563,661,759 | IssuesEvent | 2016-01-25 05:55:22 | kerubistan/kerub | https://api.github.com/repos/kerubistan/kerub | opened | Host power management | component:data processing enhancement | * Implement host power management methods (IPMI, WOL)
* Integrate into planner and executor
* allow entering host power management details on UI | 1.0 | Host power management - * Implement host power management methods (IPMI, WOL)
* Integrate into planner and executor
* allow entering host power management details on UI | process | host power management implement host power management methods ipmi wol integrate into planner and executor allow entering host power management details on ui | 1 |
19,558 | 25,882,147,989 | IssuesEvent | 2022-12-14 12:02:44 | gchq/stroom | https://api.github.com/repos/gchq/stroom | opened | Seeing `No effective streams found` errors when a ref data map contains XML data | bug f:processing | Works fine if the map contains simple string values. | 1.0 | Seeing `No effective streams found` errors when a ref data map contains XML data - Works fine if the map contains simple string values. | process | seeing no effective streams found errors when a ref data map contains xml data works fine if the map contains simple string values | 1 |
73,266 | 3,410,222,825 | IssuesEvent | 2015-12-04 19:10:46 | jamesmontemagno/Xamarin.Plugins | https://api.github.com/repos/jamesmontemagno/Xamarin.Plugins | opened | [Feature Request] Abstract Image Metadata & Return in MediaFile | enhancement Media priority-low | Originally from #76, what is requested is a way to abstract the metadata form the files into a common class that is returned with the file location in the Media File.
Things such as:
* Size
* Dimensions
* Date
* Exposure
* Camera Make
* Camera Model
* Etc.. | 1.0 | [Feature Request] Abstract Image Metadata & Return in MediaFile - Originally from #76, what is requested is a way to abstract the metadata form the files into a common class that is returned with the file location in the Media File.
Things such as:
* Size
* Dimensions
* Date
* Exposure
* Camera Make
* Camera M... | non_process | abstract image metadata return in mediafile originally from what is requested is a way to abstract the metadata form the files into a common class that is returned with the file location in the media file things such as size dimensions date exposure camera make camera model etc | 0 |
7,393 | 10,520,436,847 | IssuesEvent | 2019-09-30 01:13:08 | qgis/QGIS | https://api.github.com/repos/qgis/QGIS | closed | Aggregate processing tool - Group by expression ($geometry) doesn't work | Bug Feedback Processing | Author Name: **Brent Edwards** (Brent Edwards)
Original Redmine Issue: [21740](https://issues.qgis.org/issues/21740)
Affected QGIS version: 3.6.0
Redmine category:processing/qgis
---
As the title states, when attempting to aggregate by geometry the results are inconclusive.
I tested the following expressions on a ... | 1.0 | Aggregate processing tool - Group by expression ($geometry) doesn't work - Author Name: **Brent Edwards** (Brent Edwards)
Original Redmine Issue: [21740](https://issues.qgis.org/issues/21740)
Affected QGIS version: 3.6.0
Redmine category:processing/qgis
---
As the title states, when attempting to aggregate by geometr... | process | aggregate processing tool group by expression geometry doesn t work author name brent edwards brent edwards original redmine issue affected qgis version redmine category processing qgis as the title states when attempting to aggregate by geometry the results are inconclusive i teste... | 1 |
8,317 | 11,485,924,023 | IssuesEvent | 2020-02-11 08:53:46 | geneontology/go-ontology | https://api.github.com/repos/geneontology/go-ontology | closed | ~obsolete~ merge GO:0010204 defense response signaling pathway, resistance gene-independent | multi-species process term merge | GO:0010204 defense response signaling pathway, resistance gene-independent
14 EXP annotations
This term should be obsoleted, becasue we shouldn't define things by what they aren't.
This would seem to apply to PAMP-mediated signalling, but could also apply to the non-immune system. There should always be a mor... | 1.0 | ~obsolete~ merge GO:0010204 defense response signaling pathway, resistance gene-independent - GO:0010204 defense response signaling pathway, resistance gene-independent
14 EXP annotations
This term should be obsoleted, becasue we shouldn't define things by what they aren't.
This would seem to apply to PAMP... | process | obsolete merge go defense response signaling pathway resistance gene independent go defense response signaling pathway resistance gene independent exp annotations this term should be obsoleted becasue we shouldn t define things by what they aren t this would seem to apply to pamp mediated sig... | 1 |
10,259 | 13,110,976,751 | IssuesEvent | 2020-08-04 21:49:20 | SCIInstitute/Seg3D | https://api.github.com/repos/SCIInstitute/Seg3D | opened | Better DICOM support | feature request file import software processes usability | - [ ] Ability to separate multiple volumes in the same folder
- [ ] Read in time series data such as: DWI/DTI and fMRI (can use for registration) | 1.0 | Better DICOM support - - [ ] Ability to separate multiple volumes in the same folder
- [ ] Read in time series data such as: DWI/DTI and fMRI (can use for registration) | process | better dicom support ability to separate multiple volumes in the same folder read in time series data such as dwi dti and fmri can use for registration | 1 |
138,953 | 18,797,799,672 | IssuesEvent | 2021-11-09 01:26:46 | rgordon95/conFusionAng | https://api.github.com/repos/rgordon95/conFusionAng | opened | CVE-2021-23400 (High) detected in nodemailer-2.7.2.tgz | security vulnerability | ## CVE-2021-23400 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nodemailer-2.7.2.tgz</b></p></summary>
<p>Easy as cake e-mail sending from your Node.js applications</p>
<p>Library ho... | True | CVE-2021-23400 (High) detected in nodemailer-2.7.2.tgz - ## CVE-2021-23400 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nodemailer-2.7.2.tgz</b></p></summary>
<p>Easy as cake e-mail... | non_process | cve high detected in nodemailer tgz cve high severity vulnerability vulnerable library nodemailer tgz easy as cake e mail sending from your node js applications library home page a href path to dependency file confusionang package json path to vulnerable library con... | 0 |
18,533 | 24,553,124,969 | IssuesEvent | 2022-10-12 14:01:02 | GoogleCloudPlatform/fda-mystudies | https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies | closed | [PM] [VAPT] Red color disable icon should get displayed when admin mouse hovered on the disabled fields | Bug P2 Participant manager Process: Fixed Process: Tested QA Process: Tested dev | Red color disable icon should get displayed when the admin mouse hovered on the disabled fields
1. Participant details screen > Enrolled users > Enable invitation and Disable invitation
2. Forgot Password screen
3. My account screen | 3.0 | [PM] [VAPT] Red color disable icon should get displayed when admin mouse hovered on the disabled fields - Red color disable icon should get displayed when the admin mouse hovered on the disabled fields
1. Participant details screen > Enrolled users > Enable invitation and Disable invitation
2. Forgot Password scree... | process | red color disable icon should get displayed when admin mouse hovered on the disabled fields red color disable icon should get displayed when the admin mouse hovered on the disabled fields participant details screen enrolled users enable invitation and disable invitation forgot password screen my... | 1 |
20,615 | 27,288,630,083 | IssuesEvent | 2023-02-23 15:09:32 | googleapis/python-bigquery-sqlalchemy | https://api.github.com/repos/googleapis/python-bigquery-sqlalchemy | closed | compliance tests not running with pytest >= 7.0.0 | type: process priority: p3 api: bigquery | For some reason when the latest pytest is installed, I get
```
(compliance-3-8) (base) ➜ python-bigquery-sqlalchemy git:(tswast-prerelease) ✗ py.test -vv --junitxml=compliance_3.8_sponge_log.xml --reruns=3 --reruns-delay=60 '--only-rerun=403 Exceeded rate limits' '--only-rerun=409 Already Exists' '--only-rerun=404... | 1.0 | compliance tests not running with pytest >= 7.0.0 - For some reason when the latest pytest is installed, I get
```
(compliance-3-8) (base) ➜ python-bigquery-sqlalchemy git:(tswast-prerelease) ✗ py.test -vv --junitxml=compliance_3.8_sponge_log.xml --reruns=3 --reruns-delay=60 '--only-rerun=403 Exceeded rate limits'... | process | compliance tests not running with pytest for some reason when the latest pytest is installed i get compliance base ➜ python bigquery sqlalchemy git tswast prerelease ✗ py test vv junitxml compliance sponge log xml reruns reruns delay only rerun exceeded rate limits ... | 1 |
19,318 | 25,468,502,169 | IssuesEvent | 2022-11-25 07:57:15 | GoogleCloudPlatform/fda-mystudies | https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies | closed | [iOS] Not getting the study completion pop up in the study activities screen even though user submitted all the activities | Bug P1 iOS Process: Fixed Process: Tested QA | Not getting the study completed pop-up is not getting displayed on the study activities screen even though the user submitted all the activities present in the activities screen
Actual result:

Expe... | 2.0 | [iOS] Not getting the study completion pop up in the study activities screen even though user submitted all the activities - Not getting the study completed pop-up is not getting displayed on the study activities screen even though the user submitted all the activities present in the activities screen
Actual result:... | process | not getting the study completion pop up in the study activities screen even though user submitted all the activities not getting the study completed pop up is not getting displayed on the study activities screen even though the user submitted all the activities present in the activities screen actual result ... | 1 |
217,709 | 16,870,089,474 | IssuesEvent | 2021-06-22 02:30:06 | thesofproject/sof | https://api.github.com/repos/thesofproject/sof | opened | [BUG][ADL]dai_config error when aplaying HDMI1 on ADL | Intel Daily tests bug | **Describe the bug**
When running aplay on HDMI1 , dai_config error occured
**To Reproduce**
on ADLP_RVP_SDW, run aplay -Dhw:0,5 -r 48000 -c 2 -f S16_LE -d 10 /dev/zero -v -q
on ADLP_RVP_HDA , run aplay -Dhw:0,3 -r 48000 -c 2 -f S16_LE -d 10 /dev/zero -v -q
**Reproduction Rate**
100%
**Environment**... | 1.0 | [BUG][ADL]dai_config error when aplaying HDMI1 on ADL - **Describe the bug**
When running aplay on HDMI1 , dai_config error occured
**To Reproduce**
on ADLP_RVP_SDW, run aplay -Dhw:0,5 -r 48000 -c 2 -f S16_LE -d 10 /dev/zero -v -q
on ADLP_RVP_HDA , run aplay -Dhw:0,3 -r 48000 -c 2 -f S16_LE -d 10 /dev/zero -... | non_process | dai config error when aplaying on adl describe the bug when running aplay on dai config error occured to reproduce on adlp rvp sdw run aplay dhw r c f le d dev zero v q on adlp rvp hda run aplay dhw r c f le d dev zero v q reproduction rate ... | 0 |
240,052 | 19,989,489,444 | IssuesEvent | 2022-01-31 03:24:48 | datafuselabs/databend | https://api.github.com/repos/datafuselabs/databend | closed | Refine the stateful tests directory | C-testing C-good first issue | https://github.com/datafuselabs/databend/tree/3e1b530b9fa8ab16c140c9f4f16e582d9e768b8c/tests/suites/1_stateful
Move `12_0000_copy_s3.*` to `copy` folder, and rename to `00_0000_copy_s3`.
Move `12_0001_streaming_load.*` to `load` folder, and rename to `00_0000_streaming_load`. | 1.0 | Refine the stateful tests directory - https://github.com/datafuselabs/databend/tree/3e1b530b9fa8ab16c140c9f4f16e582d9e768b8c/tests/suites/1_stateful
Move `12_0000_copy_s3.*` to `copy` folder, and rename to `00_0000_copy_s3`.
Move `12_0001_streaming_load.*` to `load` folder, and rename to `00_0000_streaming_load`. | non_process | refine the stateful tests directory move copy to copy folder and rename to copy move streaming load to load folder and rename to streaming load | 0 |
560,511 | 16,598,521,722 | IssuesEvent | 2021-06-01 16:06:47 | appjusto/admin | https://api.github.com/repos/appjusto/admin | closed | Order situation "declined" in BO drawer | backoffice enhancement priority 0 | - [x] Show declined option;
- [x] Show declined issues (canceled). | 1.0 | Order situation "declined" in BO drawer - - [x] Show declined option;
- [x] Show declined issues (canceled). | non_process | order situation declined in bo drawer show declined option show declined issues canceled | 0 |
10,551 | 13,338,816,745 | IssuesEvent | 2020-08-28 11:46:33 | arcus-azure/arcus.messaging | https://api.github.com/repos/arcus-azure/arcus.messaging | closed | Provide catch-all message handler | area:message-processing enhancement feature | Provide a catch-all message handler that can be used in case no matching message handler was found. | 1.0 | Provide catch-all message handler - Provide a catch-all message handler that can be used in case no matching message handler was found. | process | provide catch all message handler provide a catch all message handler that can be used in case no matching message handler was found | 1 |
13,158 | 15,588,428,053 | IssuesEvent | 2021-03-18 06:22:50 | q191201771/lal | https://api.github.com/repos/q191201771/lal | closed | RTSP 1080视频花屏 | #Bug *In process *Waiting reply | ### 测试环境
- 测试版本:lal_v0.19.1_linux,默认配置
### 出现问题
- RTSP over udp 推流1080p视频:
`ffmpeg -re -stream_loop -1 -i "bbb_sunflower_1080p_30fps_normal.mp4" -an -vcodec copy -f rtsp rtsp://localhost:5544/live/test110`
- ffplay播放rtsp,看几秒钟后兔子出洞后花屏,每次重新播放花屏的时间和位置都一样。
- 转rtmp播放或者改为rtsp over tcp推流均没有问题
- RTSP over udp 推流小码流文件(s... | 1.0 | RTSP 1080视频花屏 - ### 测试环境
- 测试版本:lal_v0.19.1_linux,默认配置
### 出现问题
- RTSP over udp 推流1080p视频:
`ffmpeg -re -stream_loop -1 -i "bbb_sunflower_1080p_30fps_normal.mp4" -an -vcodec copy -f rtsp rtsp://localhost:5544/live/test110`
- ffplay播放rtsp,看几秒钟后兔子出洞后花屏,每次重新播放花屏的时间和位置都一样。
- 转rtmp播放或者改为rtsp over tcp推流均没有问题
- RTSP ov... | process | rtsp 测试环境 测试版本:lal linux 默认配置 出现问题 rtsp over udp ffmpeg re stream loop i bbb sunflower normal an vcodec copy f rtsp rtsp localhost live ffplay播放rtsp,看几秒钟后兔子出洞后花屏,每次重新播放花屏的时间和位置都一样。 转rtmp播放或者改为rtsp over tcp推流均没有问题 rtsp over udp 推流小码流文件 source flv 没有这个问题... | 1 |
192,999 | 22,216,033,451 | IssuesEvent | 2022-06-08 01:49:00 | AlexRogalskiy/github-action-json-fields | https://api.github.com/repos/AlexRogalskiy/github-action-json-fields | closed | CVE-2021-44907 (High) detected in qs-6.5.2.tgz - autoclosed | security vulnerability | ## CVE-2021-44907 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>qs-6.5.2.tgz</b></p></summary>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Lib... | True | CVE-2021-44907 (High) detected in qs-6.5.2.tgz - autoclosed - ## CVE-2021-44907 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>qs-6.5.2.tgz</b></p></summary>
<p>A querystring parser t... | non_process | cve high detected in qs tgz autoclosed cve high severity vulnerability vulnerable library qs tgz a querystring parser that supports nesting and arrays with a depth limit library home page a href path to dependency file package json path to vulnerable library nod... | 0 |
7,591 | 10,703,369,858 | IssuesEvent | 2019-10-24 09:25:39 | microsoft/vscode | https://api.github.com/repos/microsoft/vscode | closed | ShardProcess: Trying to add a disposable to a DisposableStore that has already been disposed of | bug shared-process | Saw this shutting down quickly after starting up:
```
Error: Trying to add a disposable to a DisposableStore that has already been disposed of. The added object will be leaked!
at DisposableStore.add (/home/bpasero/development/monaco/out/vs/base/common/lifecycle.js:116:30)
at EventEmitter.<anonymous> (/ho... | 1.0 | ShardProcess: Trying to add a disposable to a DisposableStore that has already been disposed of - Saw this shutting down quickly after starting up:
```
Error: Trying to add a disposable to a DisposableStore that has already been disposed of. The added object will be leaked!
at DisposableStore.add (/home/bpaser... | process | shardprocess trying to add a disposable to a disposablestore that has already been disposed of saw this shutting down quickly after starting up error trying to add a disposable to a disposablestore that has already been disposed of the added object will be leaked at disposablestore add home bpaser... | 1 |
12,537 | 14,972,532,978 | IssuesEvent | 2021-01-27 23:02:43 | panther-labs/panther | https://api.github.com/repos/panther-labs/panther | opened | Salesforce Log Puller | epic p0 team:data processing | ### Description
As an analyst, I want to be able to pull important Salesforce audit logs via a SaaS log experience.
### RFC
N/A
### Designs
TBD
### Acceptance Criteria
- step by step SaaS onboarding experience for Salesforce logs
- Agreed upon set of logs to support in MVP (after discussing with customers and lo... | 1.0 | Salesforce Log Puller - ### Description
As an analyst, I want to be able to pull important Salesforce audit logs via a SaaS log experience.
### RFC
N/A
### Designs
TBD
### Acceptance Criteria
- step by step SaaS onboarding experience for Salesforce logs
- Agreed upon set of logs to support in MVP (after discussi... | process | salesforce log puller description as an analyst i want to be able to pull important salesforce audit logs via a saas log experience rfc n a designs tbd acceptance criteria step by step saas onboarding experience for salesforce logs agreed upon set of logs to support in mvp after discussi... | 1 |
709,057 | 24,366,467,626 | IssuesEvent | 2022-10-03 15:31:50 | TheGameCreators/AGK-Studio | https://api.github.com/repos/TheGameCreators/AGK-Studio | closed | Loss of Color in TextFontImages [Classic] | bug AGK-Core Low priority | FontImages have now lost color since the 2022.09.08 update (presumably related to the known issue re: the new [Text Shader](https://forum.thegamecreators.com/thread/228674#msg2671863) commands in Classic):
<img width="641" alt="wf" src="https://user-images.githubusercontent.com/52613918/193424637-da0c655e-18e4-4ba8-a8... | 1.0 | Loss of Color in TextFontImages [Classic] - FontImages have now lost color since the 2022.09.08 update (presumably related to the known issue re: the new [Text Shader](https://forum.thegamecreators.com/thread/228674#msg2671863) commands in Classic):
<img width="641" alt="wf" src="https://user-images.githubusercontent.... | non_process | loss of color in textfontimages fontimages have now lost color since the update presumably related to the known issue re the new commands in classic img width alt wf src forum post complete with project sample win issue carries into html export et al | 0 |
60,384 | 3,125,996,295 | IssuesEvent | 2015-09-08 06:17:57 | NuGet/NuGetGallery | https://api.github.com/repos/NuGet/NuGetGallery | closed | Add Downloads by Client Report to Statistics Page | Priority - 2 | - This should show a graph.
- The data is from on a json blob created by the worker.
<!---
@huboard:{"order":4.25}
-->
| 1.0 | Add Downloads by Client Report to Statistics Page - - This should show a graph.
- The data is from on a json blob created by the worker.
<!---
@huboard:{"order":4.25}
-->
| non_process | add downloads by client report to statistics page this should show a graph the data is from on a json blob created by the worker huboard order | 0 |
23,049 | 3,755,593,109 | IssuesEvent | 2016-03-12 19:27:48 | RomanGolovanov/aMetro | https://api.github.com/repos/RomanGolovanov/aMetro | closed | Список карт для обновления при переходе через нотификацию не показывается | auto-migrated Component-Logic Priority-Medium Type-Defect | ```
What steps will reproduce the problem?
1. Переггрузить телефон;
2. Включить инет;
3. Дождаться проверки каталога, перейти по
нотификации, что есть обновления.
What is the expected output? What do you see instead?
Ожидается увидеть список массового
обновления карт. Показывается просто
список карт. Если же прилож... | 1.0 | Список карт для обновления при переходе через нотификацию не показывается - ```
What steps will reproduce the problem?
1. Переггрузить телефон;
2. Включить инет;
3. Дождаться проверки каталога, перейти по
нотификации, что есть обновления.
What is the expected output? What do you see instead?
Ожидается увидеть список ... | non_process | список карт для обновления при переходе через нотификацию не показывается what steps will reproduce the problem переггрузить телефон включить инет дождаться проверки каталога перейти по нотификации что есть обновления what is the expected output what do you see instead ожидается увидеть список ... | 0 |
21,540 | 3,518,268,932 | IssuesEvent | 2016-01-12 12:01:10 | Virtual-Labs/problem-solving-iiith | https://api.github.com/repos/Virtual-Labs/problem-solving-iiith | reopened | QA_Permutation_UI | Category :UI Defect raised on: 26-11-2015 Developed by:IIIT Hyd Release Number Severity :S3 Status :Open Version Number :1.1 | Defect Description:
In the Landing page of "Permutation" experiment, the 'Home' &'Problem Solving Lab' links are present outside of the page width instead the links should be placed within the page limit inorder to maintain the page utility .
Actual Result:
In the Landing page of "Permutation" experiment,the 'H... | 1.0 | QA_Permutation_UI - Defect Description:
In the Landing page of "Permutation" experiment, the 'Home' &'Problem Solving Lab' links are present outside of the page width instead the links should be placed within the page limit inorder to maintain the page utility .
Actual Result:
In the Landing page of "Permutatio... | non_process | qa permutation ui defect description in the landing page of permutation experiment the home problem solving lab links are present outside of the page width instead the links should be placed within the page limit inorder to maintain the page utility actual result in the landing page of permutatio... | 0 |
9,040 | 6,735,020,458 | IssuesEvent | 2017-10-18 20:11:00 | Microsoft/BotBuilder | https://api.github.com/repos/Microsoft/BotBuilder | closed | [Question] Bot posts duplicate messages when bad connectivity | .NET SDK performance question Skype | <!--
Have a question?
Ask on http://stackoverflow.com/questions/tagged/botframework using the tag "botframework".
-->
## System Information
* SDK Language: .NET
* SDK Version: v.3.9.0
* Development Environment: <!-- localhost, Auzure Bot Service, App Service, other -->
## Bot Info <!-- As regist... | True | [Question] Bot posts duplicate messages when bad connectivity - <!--
Have a question?
Ask on http://stackoverflow.com/questions/tagged/botframework using the tag "botframework".
-->
## System Information
* SDK Language: .NET
* SDK Version: v.3.9.0
* Development Environment: <!-- localhost, Auzure B... | non_process | bot posts duplicate messages when bad connectivity have a question ask on using the tag botframework system information sdk language net sdk version v development environment bot info bot name planner bot bot handle taskplannerbot app id ... | 0 |
160,985 | 20,120,376,021 | IssuesEvent | 2022-02-08 01:12:55 | arohablue/BlockDockServer | https://api.github.com/repos/arohablue/BlockDockServer | opened | postgresql-9.4.1211.jre7.jar: 2 vulnerabilities (highest severity is: 9.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>postgresql-9.4.1211.jre7.jar</b></p></summary>
<p>Java JDBC 4.1 (JRE 7+) driver for PostgreSQL database</p>
<p>Library home page: <a href="https://github.com/pgjdbc/p... | True | postgresql-9.4.1211.jre7.jar: 2 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>postgresql-9.4.1211.jre7.jar</b></p></summary>
<p>Java JDBC 4.1 (JRE 7+) driver for Postg... | non_process | postgresql jar vulnerabilities highest severity is vulnerable library postgresql jar java jdbc jre driver for postgresql database library home page a href path to dependency file blockdockserver build gradle path to vulnerable library radle caches modules ... | 0 |
155,073 | 19,765,661,807 | IssuesEvent | 2022-01-17 01:40:55 | tuanducdesign/email-sending-verification | https://api.github.com/repos/tuanducdesign/email-sending-verification | opened | CVE-2021-23424 (High) detected in ansi-html-0.0.7.tgz | security vulnerability | ## CVE-2021-23424 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ansi-html-0.0.7.tgz</b></p></summary>
<p>An elegant lib that converts the chalked (ANSI) text to HTML.</p>
<p>Library ... | True | CVE-2021-23424 (High) detected in ansi-html-0.0.7.tgz - ## CVE-2021-23424 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ansi-html-0.0.7.tgz</b></p></summary>
<p>An elegant lib that c... | non_process | cve high detected in ansi html tgz cve high severity vulnerability vulnerable library ansi html tgz an elegant lib that converts the chalked ansi text to html library home page a href path to dependency file client package json path to vulnerable library client ... | 0 |
54,213 | 23,202,492,461 | IssuesEvent | 2022-08-01 23:30:38 | ArctosDB/arctos | https://api.github.com/repos/ArctosDB/arctos | closed | Advice Request: Tracking Extinct and Endangered Species in Arctos | Function-Taxonomy/Identification Enhancement Service-related | Has anyone come up with a way to track extinct / endangered / threatened species in Arctos? Whether it is a report or project or attribute, I'm curious to know how this has been addressed.
As a part of our permit process, we report specimens in our holdings to IDNR of endangered and threatened species held in our co... | 1.0 | Advice Request: Tracking Extinct and Endangered Species in Arctos - Has anyone come up with a way to track extinct / endangered / threatened species in Arctos? Whether it is a report or project or attribute, I'm curious to know how this has been addressed.
As a part of our permit process, we report specimens in our ... | non_process | advice request tracking extinct and endangered species in arctos has anyone come up with a way to track extinct endangered threatened species in arctos whether it is a report or project or attribute i m curious to know how this has been addressed as a part of our permit process we report specimens in our ... | 0 |
19,089 | 25,140,813,109 | IssuesEvent | 2022-11-09 22:56:16 | open-telemetry/opentelemetry-collector-contrib | https://api.github.com/repos/open-telemetry/opentelemetry-collector-contrib | closed | [resourceprocessor] Specify list of resource attributes allowed to reach exporters | Stale processor/resource | **Is your feature request related to a problem? Please describe.**
As exporters can use [resource_to_telemetry_conversion](https://github.com/open-telemetry/opentelemetry-collector/blob/main/exporter/exporterhelper/README.md) to convert resource attributes into metric labels, ideally there should be a way to easily fi... | 1.0 | [resourceprocessor] Specify list of resource attributes allowed to reach exporters - **Is your feature request related to a problem? Please describe.**
As exporters can use [resource_to_telemetry_conversion](https://github.com/open-telemetry/opentelemetry-collector/blob/main/exporter/exporterhelper/README.md) to conve... | process | specify list of resource attributes allowed to reach exporters is your feature request related to a problem please describe as exporters can use to convert resource attributes into metric labels ideally there should be a way to easily filter resource attributes describe the solution you d like ... | 1 |
16,075 | 20,248,946,964 | IssuesEvent | 2022-02-14 16:07:28 | Bone008/orbiteye | https://api.github.com/repos/Bone008/orbiteye | opened | Process "Purpose" column for SATCAT data | data processing | Using the multiple separated sheets from [Celestrak](https://celestrak.com/NORAD/elements/) label the purpose of SATCAT rows where possible. | 1.0 | Process "Purpose" column for SATCAT data - Using the multiple separated sheets from [Celestrak](https://celestrak.com/NORAD/elements/) label the purpose of SATCAT rows where possible. | process | process purpose column for satcat data using the multiple separated sheets from label the purpose of satcat rows where possible | 1 |
74,934 | 9,167,723,230 | IssuesEvent | 2019-03-02 16:11:30 | boostorg/beast | https://api.github.com/repos/boostorg/beast | opened | string_base ideas | Design Feature | We can refactor `static_string`:
* Call it `char_string_base`, make it a normal class (i.e. not a template)
* Eschew `char_traits` and `CharT`, this is for `char` **only** and no locales
* Express all operations in terms of a virtual member `realloc`
* function by function compatibility with `std;:string`
* Ful... | 1.0 | string_base ideas - We can refactor `static_string`:
* Call it `char_string_base`, make it a normal class (i.e. not a template)
* Eschew `char_traits` and `CharT`, this is for `char` **only** and no locales
* Express all operations in terms of a virtual member `realloc`
* function by function compatibility with ... | non_process | string base ideas we can refactor static string call it char string base make it a normal class i e not a template eschew char traits and chart this is for char only and no locales express all operations in terms of a virtual member realloc function by function compatibility with ... | 0 |
345,618 | 24,867,565,867 | IssuesEvent | 2022-10-27 13:06:29 | HyperloopUPV-H8/ST-LIB | https://api.github.com/repos/HyperloopUPV-H8/ST-LIB | closed | Problemas y soluciones a la hora de usar la FLASH | documentation | ## Los problemas que nos podemos encontrar usando la FLASH son los siguientes:
- Lo primero, hay que tener en cuenta que la FLASH es bastante delicada, un fallo en la alimentación o que esta sea inestable durante un proceso de borrado, escritura o incluso cuando esta no esta realizando ninguna operación podría causar ... | 1.0 | Problemas y soluciones a la hora de usar la FLASH - ## Los problemas que nos podemos encontrar usando la FLASH son los siguientes:
- Lo primero, hay que tener en cuenta que la FLASH es bastante delicada, un fallo en la alimentación o que esta sea inestable durante un proceso de borrado, escritura o incluso cuando esta... | non_process | problemas y soluciones a la hora de usar la flash los problemas que nos podemos encontrar usando la flash son los siguientes lo primero hay que tener en cuenta que la flash es bastante delicada un fallo en la alimentación o que esta sea inestable durante un proceso de borrado escritura o incluso cuando esta... | 0 |
3,679 | 6,713,470,781 | IssuesEvent | 2017-10-13 13:35:53 | decidim/decidim | https://api.github.com/repos/decidim/decidim | closed | Bug when inviting moderators | component: processes in-progress type: bug | # This is a Bug Report
#### :tophat: Description
When inviting a moderator (email not associated with any account) on a participatory process the moderator gets stuck at the "Password / Confirm Password" step and is not able to validate its account.
This what the bug looks like.
 on a participatory process the moderator gets stuck at the "Password / Confirm Password" step and is not able to validate its account.
This what the bug looks like.
... | process | bug when inviting moderators this is a bug report tophat description when inviting a moderator email not associated with any account on a participatory process the moderator gets stuck at the password confirm password step and is not able to validate its account this what the bug looks like ... | 1 |
9,724 | 12,719,803,417 | IssuesEvent | 2020-06-24 09:53:32 | prisma/prisma-client-js | https://api.github.com/repos/prisma/prisma-client-js | opened | Feature Request: Using Prisma Client as query builder only and get the SQL queries like `prisma.user.findOne().getRawQuery()` | kind/feature process/candidate team/product | ## Problem
Adding this feature opens the possibility to use Prisma Client as a query builder only.
Meaning getting the SQL queries without actually hitting the database.
What Lucas wanted is to be able to visualize the query that is going to execute in some sort of playground editor.
## Suggested solution
`pri... | 1.0 | Feature Request: Using Prisma Client as query builder only and get the SQL queries like `prisma.user.findOne().getRawQuery()` - ## Problem
Adding this feature opens the possibility to use Prisma Client as a query builder only.
Meaning getting the SQL queries without actually hitting the database.
What Lucas wanted... | process | feature request using prisma client as query builder only and get the sql queries like prisma user findone getrawquery problem adding this feature opens the possibility to use prisma client as a query builder only meaning getting the sql queries without actually hitting the database what lucas wanted... | 1 |
15,918 | 20,120,969,956 | IssuesEvent | 2022-02-08 02:14:30 | streamnative/flink | https://api.github.com/repos/streamnative/flink | closed | [BUG][FLINK-24668] Pulsar consumption data repeated output | compute/data-processing type/bug | `flink-connector-pulsar` uses the `RecordsBySplits` of flink-connector-base to process data, But recordsInCurrentSplit and splitsIterator are not empty when nextSplit `splitSiterator.hasNext () = false`. | 1.0 | [BUG][FLINK-24668] Pulsar consumption data repeated output - `flink-connector-pulsar` uses the `RecordsBySplits` of flink-connector-base to process data, But recordsInCurrentSplit and splitsIterator are not empty when nextSplit `splitSiterator.hasNext () = false`. | process | pulsar consumption data repeated output flink connector pulsar uses the recordsbysplits of flink connector base to process data but recordsincurrentsplit and splitsiterator are not empty when nextsplit splitsiterator hasnext false | 1 |
115,855 | 4,683,113,168 | IssuesEvent | 2016-10-09 16:28:59 | chartjs/Chart.js | https://api.github.com/repos/chartjs/Chart.js | closed | Tooltips & x-axis mode v2.2.0 | Category: Bug Needs Investigation Priority: p1 | Hi,
1 - Tooltips arrow default position is "right" and we can see the arrow blink from the right to its calculated position during fade in and fade out animation.

2 - For bar chart, x-axis mode (thank... | 1.0 | Tooltips & x-axis mode v2.2.0 - Hi,
1 - Tooltips arrow default position is "right" and we can see the arrow blink from the right to its calculated position during fade in and fade out animation.

2 - F... | non_process | tooltips x axis mode hi tooltips arrow default position is right and we can see the arrow blink from the right to its calculated position during fade in and fade out animation for bar chart x axis mode thanks for this option mesonyx depends of stacked param if stacked is true ... | 0 |
5,030 | 7,851,532,610 | IssuesEvent | 2018-06-20 12:04:23 | allinurl/goaccess | https://api.github.com/repos/allinurl/goaccess | closed | Error in report when import multple logs | log-processing | 
When I import multiple files, the report is wrong.
It look like all of them will be count into the day when the logs was imported.
In the photo, June 18 is the day which I ra... | 1.0 | Error in report when import multple logs - 
When I import multiple files, the report is wrong.
It look like all of them will be count into the day when the logs was imported.
... | process | error in report when import multple logs when i import multiple files the report is wrong it look like all of them will be count into the day when the logs was imported in the photo june is the day which i ran command to import | 1 |
553,871 | 16,384,348,280 | IssuesEvent | 2021-05-17 08:31:22 | MathiasReker/Delfinen | https://api.github.com/repos/MathiasReker/Delfinen | opened | DisciplineModel fix | bug medium priority | Remove some of the code, maby it should be used another place
.. make sens when we need the class. | 1.0 | DisciplineModel fix - Remove some of the code, maby it should be used another place
.. make sens when we need the class. | non_process | disciplinemodel fix remove some of the code maby it should be used another place make sens when we need the class | 0 |
9,013 | 12,123,868,663 | IssuesEvent | 2020-04-22 13:23:41 | Torbjornsson/DATX05-Master_Thesis | https://api.github.com/repos/Torbjornsson/DATX05-Master_Thesis | opened | Process/Design | Section: Process | - [ ] Puzzles
- [ ] Tutorials
- [ ] Objects
- [ ] Environment
- [ ] Interactions
- [ ] Sound
- [ ] Test | 1.0 | Process/Design - - [ ] Puzzles
- [ ] Tutorials
- [ ] Objects
- [ ] Environment
- [ ] Interactions
- [ ] Sound
- [ ] Test | process | process design puzzles tutorials objects environment interactions sound test | 1 |
11,456 | 14,274,873,863 | IssuesEvent | 2020-11-22 06:54:26 | SerialLain3170/nagato | https://api.github.com/repos/SerialLain3170/nagato | opened | Flowtron: an Autoregressive Flow-based Generative Network for Text-to-Speech Synthesis | speech processing | # Overview
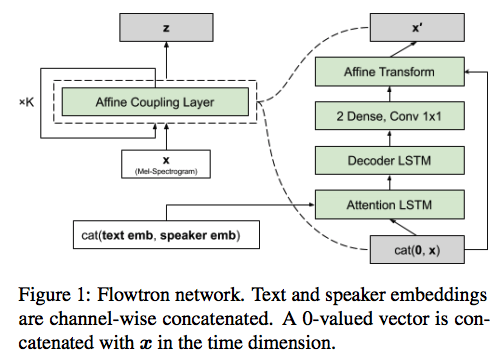
- Flowtron is autoregressive text-to-speech model that generates a sequence of mel-spectrogram frames.
- In affine coupling layer, the model incorporates speaker embe... | 1.0 | Flowtron: an Autoregressive Flow-based Generative Network for Text-to-Speech Synthesis - # Overview
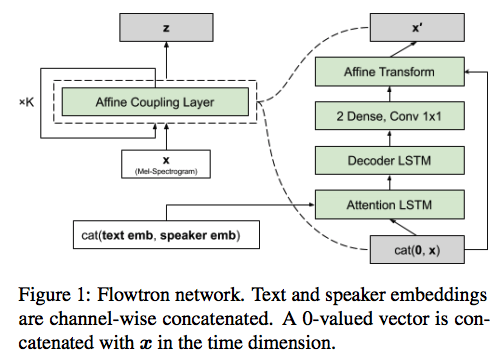
- Flowtron is autoregressive text-to-speech model that generates a sequence of... | process | flowtron an autoregressive flow based generative network for text to speech synthesis overview flowtron is autoregressive text to speech model that generates a sequence of mel spectrogram frames in affine coupling layer the model incorporates speaker embeddings and text embeddings | 1 |
22,155 | 30,695,551,392 | IssuesEvent | 2023-07-26 18:17:57 | metabase/metabase | https://api.github.com/repos/metabase/metabase | reopened | Performance regression in nested queries | Type:Bug Priority:P1 Reporting/Dashboards Querying/Nested Queries .Team/QueryProcessor :hammer_and_wrench: .Escalation | ### Describe the bug
Let's compare these 3 scenarios:
1) scenario 1
- create a question: count of people where source = 'Google', save it as a number
- add it 30 times to a dashboard, save it
- refresh

2) scenario... | 1.0 | Performance regression in nested queries - ### Describe the bug
Let's compare these 3 scenarios:
1) scenario 1
- create a question: count of people where source = 'Google', save it as a number
- add it 30 times to a dashboard, save it
- refresh

<!--session: 1680252418031-b536a5a7-94fd-4e54-924e-bf7b9d014f9f-->
<!--Version: Web v3.4.7--> | 1.0 | Formatting error in description of `add` syntax - From how the other commands are formatted, this looks like it should be formatted as bullet points
<!--session: 1680252418031-b536a5a7-94fd-4e54-924e-bf7b... | non_process | formatting error in description of add syntax from how the other commands are formatted this looks like it should be formatted as bullet points | 0 |
15,658 | 19,846,969,633 | IssuesEvent | 2022-01-21 07:53:45 | ooi-data/CE06ISSM-MFD37-03-DOSTAD000-recovered_host-dosta_abcdjm_ctdbp_dcl_instrument_recovered | https://api.github.com/repos/ooi-data/CE06ISSM-MFD37-03-DOSTAD000-recovered_host-dosta_abcdjm_ctdbp_dcl_instrument_recovered | opened | 🛑 Processing failed: ValueError | process | ## Overview
`ValueError` found in `processing_task` task during run ended on 2022-01-21T07:53:44.982293.
## Details
Flow name: `CE06ISSM-MFD37-03-DOSTAD000-recovered_host-dosta_abcdjm_ctdbp_dcl_instrument_recovered`
Task name: `processing_task`
Error type: `ValueError`
Error message: not enough values to unpack (exp... | 1.0 | 🛑 Processing failed: ValueError - ## Overview
`ValueError` found in `processing_task` task during run ended on 2022-01-21T07:53:44.982293.
## Details
Flow name: `CE06ISSM-MFD37-03-DOSTAD000-recovered_host-dosta_abcdjm_ctdbp_dcl_instrument_recovered`
Task name: `processing_task`
Error type: `ValueError`
Error messag... | process | 🛑 processing failed valueerror overview valueerror found in processing task task during run ended on details flow name recovered host dosta abcdjm ctdbp dcl instrument recovered task name processing task error type valueerror error message not enough values to unpack exp... | 1 |
21,399 | 29,202,233,769 | IssuesEvent | 2023-05-21 00:38:03 | devssa/onde-codar-em-salvador | https://api.github.com/repos/devssa/onde-codar-em-salvador | closed | [Santa Lúcia, Belo Horizonte] Flutter Developer na Coodesh | SALVADOR MOBILE FIREBASE REQUISITOS IOS ANDROID PROCESSOS GITHUB FLUTTER AMP UMA DART MANUTENÇÃO ACESSIBILIDADE ALOCADO Stale | ## Descrição da vaga:
Esta é uma vaga de um parceiro da plataforma Coodesh, ao candidatar-se você terá acesso as informações completas sobre a empresa e benefícios.
Fique atento ao redirecionamento que vai te levar para uma url [https://coodesh.com](https://coodesh.com/vagas/desenvolvedor-flutter-165642989?utm_s... | 1.0 | [Santa Lúcia, Belo Horizonte] Flutter Developer na Coodesh - ## Descrição da vaga:
Esta é uma vaga de um parceiro da plataforma Coodesh, ao candidatar-se você terá acesso as informações completas sobre a empresa e benefícios.
Fique atento ao redirecionamento que vai te levar para uma url [https://coodesh.com](ht... | process | flutter developer na coodesh descrição da vaga esta é uma vaga de um parceiro da plataforma coodesh ao candidatar se você terá acesso as informações completas sobre a empresa e benefícios fique atento ao redirecionamento que vai te levar para uma url com o pop up personalizado de candidatura 👋 ... | 1 |
5,638 | 8,494,548,252 | IssuesEvent | 2018-10-28 22:31:35 | P0cL4bs/WiFi-Pumpkin | https://api.github.com/repos/P0cL4bs/WiFi-Pumpkin | closed | Device not showing in Pumpkin device list | enhancement in process priority solved | #### Please tell us details about your environment.
* Card wireless adapters name (please check if support AP/mode):
* Version used tool:
* Virtual Machine (yes or no and which):
* Operating System and version:
## What's the problem (or question)?
I've got Kali 2017.3 on a Raspberry Pi 3
I've ran the foll... | 1.0 | Device not showing in Pumpkin device list - #### Please tell us details about your environment.
* Card wireless adapters name (please check if support AP/mode):
* Version used tool:
* Virtual Machine (yes or no and which):
* Operating System and version:
## What's the problem (or question)?
I've got Kali 2... | process | device not showing in pumpkin device list please tell us details about your environment card wireless adapters name please check if support ap mode version used tool virtual machine yes or no and which operating system and version what s the problem or question i ve got kali ... | 1 |
727,753 | 25,045,830,807 | IssuesEvent | 2022-11-05 08:15:51 | googleapis/nodejs-ai-platform | https://api.github.com/repos/googleapis/nodejs-ai-platform | opened | AI platform feature values apis: "before all" hook: should create the perm_users entity type for "should import feature values" failed | type: bug priority: p1 flakybot: issue | This test failed!
To configure my behavior, see [the Flaky Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/main/packages/flakybot).
If I'm commenting on this issue too often, add the `flakybot: quiet` label and
I will stop commenting.
---
commit: 9345b15fcc22f60f00cd50442403fc1af4fabe71
b... | 1.0 | AI platform feature values apis: "before all" hook: should create the perm_users entity type for "should import feature values" failed - This test failed!
To configure my behavior, see [the Flaky Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/main/packages/flakybot).
If I'm commenting on t... | non_process | ai platform feature values apis before all hook should create the perm users entity type for should import feature values failed this test failed to configure my behavior see if i m commenting on this issue too often add the flakybot quiet label and i will stop commenting commit buildurl ... | 0 |
15,128 | 18,872,366,761 | IssuesEvent | 2021-11-13 12:14:13 | RobertCraigie/prisma-client-py | https://api.github.com/repos/RobertCraigie/prisma-client-py | closed | Type validator is broken on python3.9.0-1 | bug/2-confirmed kind/bug process/candidate | <!--
Thanks for helping us improve Prisma Client Python! 🙏 Please follow the sections in the template and provide as much information as possible about your problem, e.g. by enabling additional logging output.
See https://prisma-client-py.readthedocs.io/en/latest/logging/ for how to enable additional logging outpu... | 1.0 | Type validator is broken on python3.9.0-1 - <!--
Thanks for helping us improve Prisma Client Python! 🙏 Please follow the sections in the template and provide as much information as possible about your problem, e.g. by enabling additional logging output.
See https://prisma-client-py.readthedocs.io/en/latest/logging... | process | type validator is broken on thanks for helping us improve prisma client python 🙏 please follow the sections in the template and provide as much information as possible about your problem e g by enabling additional logging output see for how to enable additional logging output bug d... | 1 |
345,423 | 30,810,449,434 | IssuesEvent | 2023-08-01 10:01:23 | wazuh/wazuh | https://api.github.com/repos/wazuh/wazuh | closed | Release 4.5.0 - Alpha 1 - Integration tests | type/test level/task | # Description
| Wazuh QA: Branch | Wazuh QA: Commit | Wazuh: Tag | Wazuh: Commit |
|:--:|:--:|:--:|:--:|
| `v4.5.0-alpha1`| https://github.com/wazuh/wazuh-qa/commit/ede149c9ab767d23d3d4f9ca461186dc660e45a6 | `v4.5.0-alpha1` |https://github.com/wazuh/wazuh/commit/39df1e74bfd035fea8948191ae195fc17eb7e2f3 |
We a... | 1.0 | Release 4.5.0 - Alpha 1 - Integration tests - # Description
| Wazuh QA: Branch | Wazuh QA: Commit | Wazuh: Tag | Wazuh: Commit |
|:--:|:--:|:--:|:--:|
| `v4.5.0-alpha1`| https://github.com/wazuh/wazuh-qa/commit/ede149c9ab767d23d3d4f9ca461186dc660e45a6 | `v4.5.0-alpha1` |https://github.com/wazuh/wazuh/commit/39df1... | non_process | release alpha integration tests description wazuh qa branch wazuh qa commit wazuh tag wazuh commit we are going to check that the integration tests of the branch of wazuh qa work correctly using the version of wa... | 0 |
8,224 | 11,410,593,309 | IssuesEvent | 2020-02-01 00:03:23 | parcel-bundler/parcel | https://api.github.com/repos/parcel-bundler/parcel | closed | CSS glob import breaking on new file | :bug: Bug CSS Preprocessing Stale | # 🐛 bug report
Parcel throws an error when adding a new file whilst using glob imports in css files
## 🎛 Configuration (.babelrc, package.json, cli command)
Out of the box
## 🤔 Expected Behavior
Reloads watcher when new file is added in the globbed css import
## 😯 Current Behavior
Parcel throw... | 1.0 | CSS glob import breaking on new file - # 🐛 bug report
Parcel throws an error when adding a new file whilst using glob imports in css files
## 🎛 Configuration (.babelrc, package.json, cli command)
Out of the box
## 🤔 Expected Behavior
Reloads watcher when new file is added in the globbed css import
... | process | css glob import breaking on new file 🐛 bug report parcel throws an error when adding a new file whilst using glob imports in css files 🎛 configuration babelrc package json cli command out of the box 🤔 expected behavior reloads watcher when new file is added in the globbed css import ... | 1 |
17,351 | 23,173,027,310 | IssuesEvent | 2022-07-31 01:57:07 | lynnandtonic/nestflix.fun | https://api.github.com/repos/lynnandtonic/nestflix.fun | closed | Add Olympus: The Gods' House from “Reality Z” | suggested title in process | Please add as much of the following info as you can:
Title: Olympus: The Gods' House
Type (film/tv show): TV show - reality (foreign - Brazilian)
Film or show in which it appears: Reality Z
Is the parent film/show streaming anywhere? Yes - Netflix
About when in the parent film/show does it appear? Pepper... | 1.0 | Add Olympus: The Gods' House from “Reality Z” - Please add as much of the following info as you can:
Title: Olympus: The Gods' House
Type (film/tv show): TV show - reality (foreign - Brazilian)
Film or show in which it appears: Reality Z
Is the parent film/show streaming anywhere? Yes - Netflix
About whe... | process | add olympus the gods house from “reality z” please add as much of the following info as you can title olympus the gods house type film tv show tv show reality foreign brazilian film or show in which it appears reality z is the parent film show streaming anywhere yes netflix about whe... | 1 |
6,085 | 8,941,487,170 | IssuesEvent | 2019-01-24 04:45:20 | googleapis/nodejs-compute | https://api.github.com/repos/googleapis/nodejs-compute | closed | License does not specify copyright correctly | type: process | Your [license](https://github.com/googleapis/nodejs-compute/blob/ee962dd9d1b5b068d5db6a7745cc0d722ac28ba4/LICENSE#L190) still says `Copyright [yyyy] [name of copyright owner]`. I think this needs to be updated. | 1.0 | License does not specify copyright correctly - Your [license](https://github.com/googleapis/nodejs-compute/blob/ee962dd9d1b5b068d5db6a7745cc0d722ac28ba4/LICENSE#L190) still says `Copyright [yyyy] [name of copyright owner]`. I think this needs to be updated. | process | license does not specify copyright correctly your still says copyright i think this needs to be updated | 1 |
112,413 | 17,089,599,716 | IssuesEvent | 2021-07-08 15:43:26 | turkdevops/atom | https://api.github.com/repos/turkdevops/atom | closed | CVE-2020-15168 (Medium) detected in node-fetch-1.7.3.tgz - autoclosed | security vulnerability | ## CVE-2020-15168 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-fetch-1.7.3.tgz</b></p></summary>
<p>A light-weight module that brings window.fetch to node.js and io.js</p>
<p... | True | CVE-2020-15168 (Medium) detected in node-fetch-1.7.3.tgz - autoclosed - ## CVE-2020-15168 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-fetch-1.7.3.tgz</b></p></summary>
<p>A ... | non_process | cve medium detected in node fetch tgz autoclosed cve medium severity vulnerability vulnerable library node fetch tgz a light weight module that brings window fetch to node js and io js library home page a href path to dependency file atom package json path to vulner... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.